-
 @ 94215f42:7681f622
2025-05-16 08:18:52
@ 94215f42:7681f622
2025-05-16 08:18:52Value Creation at the Edge
The conversation around artificial intelligence has largely centered on the technology itself, the capabilities of large language models, the race for more parameters, and the competition between AI companies.
He with the most data / biggest model / biggest platform wins all.
As we're been exploring in recent "Good Stuff" podcasts, the true business model of AI may be much more straightforward. AI is after all a productivity tool with little technical moat, in fact the existence of AI coding and learning tools quickly chop away at this moat even quicker!.\ \ We believe that the it's about transforming traditional human heavy businesses by dramatically reducing operational costs while maintaining or increasing output.
AI is poised to create value not primarily for AI companies themselves, but for businesses that effectively implement AI to transform their operations, particularly small, local businesses that can become extraordinarily efficient through AI adoption.
The Value Shift: From AI Companies to AI-Enabled Traditional Businesses
A central insight from episode 1 of the podcast series, is that the value of AI isn't likely to accrue primarily to companies like OpenAI or other AI technology providers. Instead, the real winners will be traditional service businesses that can leverage AI to transform their operations and cost structures.
"I think we're gonna see this shift to traditional service businesses... that traditionally have pretty fixed low margins because of a dependency on language-heavy workflows that require a lot of humans as the medium of intelligence in the business."
The opportunity here is to use AI to manage the language dependency and shift the moments of intelligence, that currently exist in the heads of our staff, into software that can run 24x7 for fractions of a cost.\ \ The real limiting factor here is less a magic AGI, but instead detailed thinking and process redesign to move humans to the edge of the process. As it turns out if we think through what each person is doing in detail we see the specific decisions, outputs, moments of intelligence are actually quite constrained and can be replicated in LLM's if we break them down to a low enough level of fidelity and take each decisions one step at a time.\ \ The result? Businesses that have traditionally operated with fixed, low margins can potentially achieve "software-style margins" by dramatically reducing their operational expenses.
Transforming Traditional Service Businesses
We have developed three key heuristics for identifying businesses that could benefit most from AI transformation:
-
Language Intensity: Businesses where much of the work involves processing language (reading, writing, communicating). Language in, language out. If you are sat in a chair and typing all day, this could be you.
-
Labor Component: Where we see this language intensity so we find many people performing similar, standardized roles. For examples, if we have four people in the same role this is a big clue we have good process, checklists, role descriptions etc for how the work can be done in order to replicate work across multiple people.
-
Load in the Business: Taking these processes into account, what amount of the operational expense of the business do they represent? Where these language and labor-intensive operations represent a significant portion of the business cost, we can see there will be significant return.
Traditional service businesses that match these criteria—legal firms, accounting practices, consulting agencies, contract engineering, design agencies and others—could see dramatic transformations through AI implementation.
By automating these language-heavy processes, businesses can potentially reduce operational costs by 50-80% while maintaining similar levels of output.
The Power of Small
We believe that small businesses may have an inherent advantage in this transformation. While large enterprises face significant barriers to reducing their workforce (political pressure, media scrutiny, organizational complexity), smaller businesses can adapt more quickly and focus on growth rather than just cost-cutting.
If I'm in a 20,000 person business and I need to remove 10,000 people... that's hard. You can't do this without sending political shock waves in your local community.
If I'm a 10 person business and I need to double my revenue, nobody gives a shit. I can just do it.
For small businesses, AI removes growth constraints. When adding the "21st person" no longer represents a significant capital investment, small businesses can scale much more efficiently:
If the next nominal client that you onboard doesn't actually cause you any more additional pain, if you don't need to hire more people to service that client... you just take off the brakes off from a growth perspective.
This gives small business a unique advantage in capitalizing on AI.
From "Bionic Humans" to "Humans at the Edge"
We currently see this integration to business happening in one of two models:
-
The Bionic Human: Equipping workers with AI tools to make them more productive.
-
Human at the Edge: Redesigning processes to be AI-native, with humans entering the process only when needed (and often facilitated by bitcoin payments).
While many businesses are focused on the first approach and it can certainly see returns, it is still a process constrained by the human input. The real value unlock comes from fundamentally redesigning business processes with AI at the core.
Now we can purchase intelligence in buckets of $0.02 API calls, how would we operate different?
This represents a profound shift in how we think about work and processes. Rather than humans being central to processes with tools supporting them, AI becomes the backbone of operations with humans providing input only at critical junctures.
This is "a complete mental shift" that challenges our fundamental assumptions about how businesses operate. The human becomes "the interface with the real world" for AI systems rather than the primary processor of information and decision-maker.
The Value Trap: Understanding the Competitive Dynamic
So what happens next? Here we have developed the concept of the Value Trap to explain how the competitive landscape will evolve as AI adoption increases..\ \

Initially, early adopters of AI and "Human at the Edge" business processes, will see dramatic benefits.
If your costs have dropped from 90 to 20 this creates an immediate competitive advantage where the early adopter is "now making 80 units of profit versus your 10 units of profit.
They gain massive pricing power in the industry and can compete for growth with an unfair advantage.
Over time, and here we believe this is likely a 5-10 year period although we believe the quicker side, competitive pressures will erode these advantages.\ \ As competitors adopt similar AI strategies, price competition will intensify, and revenues will decline. The business that initially saw its costs drop from 90 to 20 units might see its revenue decline from 100 to 30 units, resulting in similar margins but much lower overall revenue, often destroying the enterprise value of the company at these new revenue / profit levels!
This evolution creates an imperative for businesses to adopt AI early, not just to maintain perpetual advantage, but simply to survive the transition. Worse they're hit with a second challenge of the value trap, how do I keep hold of the value I generate along the way.\ \ If you're reading this on Nostr you may already suspect a way out of this value trap.\ \ If not I would invite you to consider storing the immediate short term returns you pull forwards in something that would be inflation resistant, hard to seize and ideally portable.\ \ We refer to this as a 'The big orange arbitrage".
Implications for Business Owners and Capital Allocators
For business owners, especially those running small to medium-sized enterprises, the message is clear: understand how AI could transform your industry and begin planning your transition now.\ \ This might involve creating an "AI-native twin" of your current business—similar to how Netflix developed streaming alongside its DVD business—to eventually replace your current operations. If you want help please ask, I heavily favor more small businesses in the world and would love to help make this a reality.
For capital allocation, the emerging opportunity we see if in "transformation led private equity". The acquisition of traditional service businesses and applying AI to dramatically reduce operational costs and increase enterprise value.\ \ This approach treats AI not as a product but as a transformation strategy for existing businesses with proven product-market fit.
Transformation led PE is venture style returns without the risk of product market fit.
So the lesson?
The business model of AI isn't all about selling AI technology, adding a RAG chatbot to a new DB or collecting everyone's data.\ \ Consider the humble cash flow business, use AI to transform the operational processes and save into everyone's favorite orange coin.
-
-
 @ ee6ea13a:959b6e74
2025-05-13 21:29:02
@ ee6ea13a:959b6e74
2025-05-13 21:29:02Reposted without permission from Business Insider.
Bitcoin Is A Joke
Joe Weisenthal Nov 6, 2013, 10:42 PM UTC

REUTERS/Eliana Aponte
Bitcoin is back in the news, as the digital currency has surged to new all-time highs in recent weeks.
A few weeks ago, it was just above $100. Today it's over $260.
This surge has prompted Timothy B Lee at The Washington Post to ask whether those who have called it a bubble in the past should retract and admit that they were wrong.
Well I'm not totally sure if I've called it a bubble, but I have spoken negatively of it, and I'll say that I still think it's a joke, and probably in a bubble.
Now first of all, I find the premise of Lee's post to be hilarious. The currency has been surging several percent every day lately, and that's evidence that it's not in a bubble?
Before going on, I want to be clear that saying something is a bubble is not saying it will go down. It could go to $500 or $1000 or $10,000. That's the nature of manias.
But make no mistake, Bitcoin is not the currency of the future. It has no intrinsic value.
Now this idea of "intrinsic value" when it comes to currency bothers people, and Bitcoin Bugs will immediately ask why the U.S. dollar has intrinsic value. There's an answer to that. The U.S. Dollar has intrinsic value because the U.S. government which sets the laws of doing business in the United States says it has intrinsic value. If you want to conduct commerce in the United States you have to pay taxes, and there's only one currency you're allowed to pay taxes in: U.S. dollars. There's no getting around this fact. Furthermore, if you want to use the banking system at all, there's no choice but to use U.S. dollars, because that's the currency of the Fed which is behind the whole thing.
On top of all these laws requiring the U.S. dollar to be used, the United States has a gigantic military that can force people around the world to use dollars (if it came to that) so yes, there's a lot of real-world value behind greenbacks.
Bitcoin? Nada. There's nothing keeping it being a thing. If people lose faith in it, it's over. Bitcoin is fiat currency in the most literal sense of the word.
But it gets worse. Bitcoin is mostly just a speculative vehicle. Yes, there are PR stunts about bars and other shops accepting bitcoins. And there is a Bitcoin ATM for some reason. But mostly Bitcoin is a speculative vehicle. And really, you'd be insane to actually conduct a sizable amount of commerce in bitcoins. That's because the price swings so wildly, that the next day, there's a good chance that one of the parties will have gotten royally screwed. Either the purchaser of the good will have ended up totally blowing a huge opportunity (by not holding longer) or the seller will be totally screwed (if Bitcoin instantly plunges). The very volatility that excited people to want to play the Bitcoin game is death when it comes to real transactions in the real world.
Again, Bitcoin might go up a lot more before it ultimately ends. That's the nature of bubbles. The dotcom bubble crashed a bunch of times on its way up. Then one day it ended. The same will happen with this.
In the meantime, have fun speculating!
-
 @ 374ee93a:36623347
2025-05-13 11:47:55
@ 374ee93a:36623347
2025-05-13 11:47:55Chef's notes
Lovely tart rhubarb jam with the extra firey kick of fresh root ginger.
Technically a vegetable rhubarb has low pectin content so be sure to include a high pectin fruit such as lemon/cooking apple/redcurrant/gooseberry. It also quite watery so we use a slightly higher fruit to sugar ratio (1.2:1) and evaporate off some water at the beginning.
Testing for setting point: put a saucer in the freezer to chill whilst cooking the fruit, after 5 mins of a high boil with the sugar put a small blob of jam on the cold saucer and return to the freezer for 2 minutes. If the jam forms a solid wrinkle when pushed with a spoon it is ready, if it is runny continue cooking and retest every 5 mins
The recipe can be halved for a small batch but if you have lots of rhubarb to process it is better to cook double batches in separate pans because it will take much longer to heat through, this affects the colour and flavour - the jam will taste warm and mellow rather than zingy
Sterilise glass jars in a 120c oven and pot the jam hot leaving 1/4 inch head space, it will keep for 5 years unopened if the lids are well sealed and does not require water bath canning
Details
- ⏲️ Prep time: 20 mins
- 🍳 Cook time: 30 mins
- 🍽️ Servings: 6 (jars)
Ingredients
- 1.2kg Rhubarb
- 200g Grated Root Ginger
- 100g Chopped Crystalised Ginger
- 1kg Sugar
- 1 Lemon
Directions
- Chop the rhubarb into 1/2 inch pieces, peel and finely grate the fresh root ginger, chop crystalised ginger into tiny bits. Juice and quarter a lemon (discard pips) and add all these to a pan with a small amount of water
- Simmer gently for 20 mins until the lemon and rhubarb are soft then add the sugar, stir until fully dissolved
- Boil on high to reach setting point, usually at 105 degrees c or when a small blob of jam wrinkles on a cold plate instead of being runny
- Remove the lemon pieces and pot into sterilised jars
-
 @ 95543309:196c540e
2025-05-11 12:42:09
@ 95543309:196c540e
2025-05-11 12:42:09Lets see if this works with the blossom upload and without markdown hassle.
:cat:

https://blossom.primal.net/73a099f931366732c18dd60da82db6ef65bb368eb96756f07d9fa7a8a3644009.mp4
-
 @ e39333da:7c66e53a
2025-05-16 13:20:33
@ e39333da:7c66e53a
2025-05-16 13:20:33::youtube{#Pex7jW3Tqwo}
Developer SHIFT UP has announced that their latest titled, Stellar Blade, that was released on PS5 on the 2024, will release on PC via Steam and EGS on the 11th of June 2025.
The game will be priced at $60, and $80 for the edition of the game that includes the 'Twin Expansion Pack', which includes the NieR: Automata DLC and the Goddess of Victory: Nikke DLC, and a key to redeem a Stellar Blade costume in the developer's previous Free-to-Play title Goddess of Victory: Nikke.
The trailer released to announce said release date also showcases the changes the made for the game and highlight PC specific enhancements, support, and options.
It's worth noting, in terms of negative news that tagged along with this, that the game will have Denuvo running, which there are evidence that decreases a game's performance, and may prevent you from playing the game offline. The game will also have an optional PSN account login, and because of this, the game is not available for purchase in around 130 countries. There's also an exclusive outfit locked behind a PSN-to-Steam account linking.

Here's the system requirements:
| | Minimum | Recommended | High | Very High | | ----------------------- | ----------------------------------------------------- | ------------------------------------------------------- | ------------------------------------------------------- | ------------------------------------------------- | | Average Performance | 1080P at 60 frames per second | 1440P at 60 frames per second | 1440P at 60 frames per second | 4K at 60 frames per second | | Graphic Presets | Low | Medium | High | Very High | | CPU | Intel Core i5-7600K AMD Ryzen 5 1600X | Intel Core i5-8400 AMD Ryzen 5 3600X | Intel Core i5-8400 AMD Ryzen 5 3600X | Intel Core i5-8400 AMD Ryzen 5 3600X | | GPU | NVIDIA GeForce GTX 1060 6GB AMD Radeon RX 580 8GB | NVIDIA GeForce RTX 2060 SUPER AMD Radeon RX 5700 XT | NVIDIA GeForce RTX 2070 SUPER AMD Radeon RX 6700 XT | NVIDIA GeForce RTX 3080 AMD Radeon RX 7900 XT | | RAM | 16GB | 16GB | 16GB | 16GB | | Storage | 75GB HDD (SSD Recommended) | 75GB SSD | 75GB SSD | 75GB SSD | | OS | Windows 10 64-bit | Windows 10 64-bit | Windows 10 64-bit | Windows 10 64-bit |
-
 @ 84b0c46a:417782f5
2025-05-16 13:09:31
@ 84b0c46a:417782f5
2025-05-16 13:09:31₍ ・ᴗ・ ₎ ₍ ・ᴗ・ ₎₍ ・ᴗ・ ₎
-
 @ 7459d333:f207289b
2025-05-10 10:38:56
@ 7459d333:f207289b
2025-05-10 10:38:56Description: Just as Bitcoin enabled sovereignty over money, a decentralized shipping protocol would enable sovereignty over trade. An LN/Bisq inspired shipping protocol could create an unstoppable free market.
Bitcoin gave us monetary sovereignty, freeing us from central bank manipulation, inflation, and censorship. But there's a missing link in our freedom journey: the physical world of goods.
The Problem: Even with Bitcoin, global trade remains at the mercy of: - Arbitrary tariffs and import restrictions - Political censorship of goods - Privacy invasion of shipping information - Centralized shipping carriers
The Vision: A decentralized shipping protocol with these properties:
- "Onion-routed" packages: Each carrier only knows the previous and next hop
- Bitcoin-secured multi-sig escrow: Funds locked until package delivery confirmed
- Incentive alignment: Carriers set their own fees based on risk assessment
- Privacy tiers: Options for inspected vs. sealed packages with appropriate pricing
- End-to-end sovereignty: Sender and receiver maintain control, intermediate carriers just fulfill their role
How it could work:
- Sender creates shipping request with package details and destination
- Protocol finds optimal route through independent carriers
- Each hop secured by multi-sig deposits larger than package value
- Carriers only see next hop, not ultimate destination
- Reputation systems and economic incentives maintain integrity
This creates a free market where any individual can participate as a carrier, earning Bitcoin for facilitating trade. Just like Lightning Network nodes, anyone can open "channels" with trusted partners.
Impact: This would enable true free market principles globally, making artificial trade barriers obsolete and empowering individuals to engage in voluntary exchange regardless of geographic or political boundaries.
There are a lot of challenges. But the first question is if this is a real problem and if its worth solving it.
What components would need development first? How would you solve the physical handoff challenges?
originally posted at https://stacker.news/items/976326
-
 @ 21335073:a244b1ad
2025-05-09 13:56:57
@ 21335073:a244b1ad
2025-05-09 13:56:57Someone asked for my thoughts, so I’ll share them thoughtfully. I’m not here to dictate how to promote Nostr—I’m still learning about it myself. While I’m not new to Nostr, freedom tech is a newer space for me. I’m skilled at advocating for topics I deeply understand, but freedom tech isn’t my expertise, so take my words with a grain of salt. Nothing I say is set in stone.
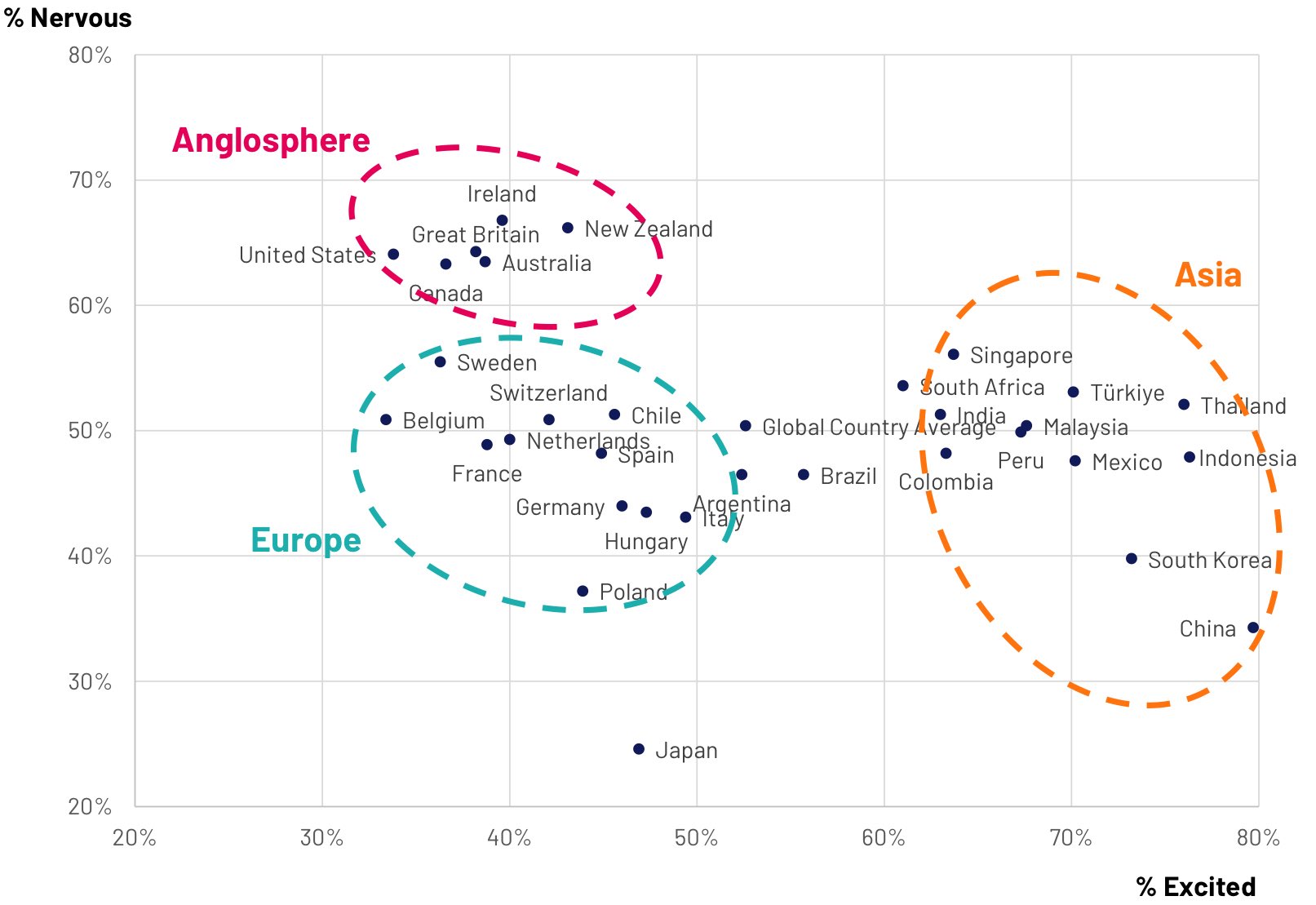
Those who need Nostr the most are the ones most vulnerable to censorship on other platforms right now. Reaching them requires real-time awareness of global issues and the dynamic relationships between governments and tech providers, which can shift suddenly. Effective Nostr promoters must grasp this and adapt quickly.
The best messengers are people from or closely tied to these at-risk regions—those who truly understand the local political and cultural dynamics. They can connect with those in need when tensions rise. Ideal promoters are rational, trustworthy, passionate about Nostr, but above all, dedicated to amplifying people’s voices when it matters most.
Forget influencers, corporate-backed figures, or traditional online PR—it comes off as inauthentic, corny, desperate and forced. Nostr’s promotion should be grassroots and organic, driven by a few passionate individuals who believe in Nostr and the communities they serve.
The idea that “people won’t join Nostr due to lack of reach” is nonsense. Everyone knows X’s “reach” is mostly with bots. If humans want real conversations, Nostr is the place. X is great for propaganda, but Nostr is for the authentic voices of the people.
Those spreading Nostr must be so passionate they’re willing to onboard others, which is time-consuming but rewarding for the right person. They’ll need to make Nostr and onboarding a core part of who they are. I see no issue with that level of dedication. I’ve been known to get that way myself at times. It’s fun for some folks.
With love, I suggest not adding Bitcoin promotion with Nostr outreach. Zaps already integrate that element naturally. (Still promote within the Bitcoin ecosystem, but this is about reaching vulnerable voices who needed Nostr yesterday.)
To promote Nostr, forget conventional strategies. “Influencers” aren’t the answer. “Influencers” are not the future. A trusted local community member has real influence—reach them. Connect with people seeking Nostr’s benefits but lacking the technical language to express it. This means some in the Nostr community might need to step outside of the Bitcoin bubble, which is uncomfortable but necessary. Thank you in advance to those who are willing to do that.
I don’t know who is paid to promote Nostr, if anyone. This piece isn’t shade. But it’s exhausting to see innocent voices globally silenced on corporate platforms like X while Nostr exists. Last night, I wondered: how many more voices must be censored before the Nostr community gets uncomfortable and thinks creatively to reach the vulnerable?
A warning: the global need for censorship-resistant social media is undeniable. If Nostr doesn’t make itself known, something else will fill that void. Let’s start this conversation.
-
 @ d61f3bc5:0da6ef4a
2025-05-06 01:37:28
@ d61f3bc5:0da6ef4a
2025-05-06 01:37:28I remember the first gathering of Nostr devs two years ago in Costa Rica. We were all psyched because Nostr appeared to solve the problem of self-sovereign online identity and decentralized publishing. The protocol seemed well-suited for textual content, but it wasn't really designed to handle binary files, like images or video.
The Problem
When I publish a note that contains an image link, the note itself is resilient thanks to Nostr, but if the hosting service disappears or takes my image down, my note will be broken forever. We need a way to publish binary data without relying on a single hosting provider.
We were discussing how there really was no reliable solution to this problem even outside of Nostr. Peer-to-peer attempts like IPFS simply didn't work; they were hopelessly slow and unreliable in practice. Torrents worked for popular files like movies, but couldn't be relied on for general file hosting.
Awesome Blossom
A year later, I attended the Sovereign Engineering demo day in Madeira, organized by Pablo and Gigi. Many projects were presented over a three hour demo session that day, but one really stood out for me.
Introduced by hzrd149 and Stu Bowman, Blossom blew my mind because it showed how we can solve complex problems easily by simply relying on the fact that Nostr exists. Having an open user directory, with the corresponding social graph and web of trust is an incredible building block.
Since we can easily look up any user on Nostr and read their profile metadata, we can just get them to simply tell us where their files are stored. This, combined with hash-based addressing (borrowed from IPFS), is all we need to solve our problem.
How Blossom Works
The Blossom protocol (Blobs Stored Simply on Mediaservers) is formally defined in a series of BUDs (Blossom Upgrade Documents). Yes, Blossom is the most well-branded protocol in the history of protocols. Feel free to refer to the spec for details, but I will provide a high level explanation here.
The main idea behind Blossom can be summarized in three points:
- Users specify which media server(s) they use via their public Blossom settings published on Nostr;
- All files are uniquely addressable via hashes;
- If an app fails to load a file from the original URL, it simply goes to get it from the server(s) specified in the user's Blossom settings.
Just like Nostr itself, the Blossom protocol is dead-simple and it works!
Let's use this image as an example:
 If you look at the URL for this image, you will notice that it looks like this:
If you look at the URL for this image, you will notice that it looks like this:blossom.primal.net/c1aa63f983a44185d039092912bfb7f33adcf63ed3cae371ebe6905da5f688d0.jpgAll Blossom URLs follow this format:
[server]/[file-hash].[extension]The file hash is important because it uniquely identifies the file in question. Apps can use it to verify that the file they received is exactly the file they requested. It also gives us the ability to reliably get the same file from a different server.
Nostr users declare which media server(s) they use by publishing their Blossom settings. If I store my files on Server A, and they get removed, I can simply upload them to Server B, update my public Blossom settings, and all Blossom-capable apps will be able to find them at the new location. All my existing notes will continue to display media content without any issues.
Blossom Mirroring
Let's face it, re-uploading files to another server after they got removed from the original server is not the best user experience. Most people wouldn't have the backups of all the files, and/or the desire to do this work.
This is where Blossom's mirroring feature comes handy. In addition to the primary media server, a Blossom user can set one one or more mirror servers. Under this setup, every time a file is uploaded to the primary server the Nostr app issues a mirror request to the primary server, directing it to copy the file to all the specified mirrors. This way there is always a copy of all content on multiple servers and in case the primary becomes unavailable, Blossom-capable apps will automatically start loading from the mirror.
Mirrors are really easy to setup (you can do it in two clicks in Primal) and this arrangement ensures robust media handling without any central points of failure. Note that you can use professional media hosting services side by side with self-hosted backup servers that anyone can run at home.
Using Blossom Within Primal
Blossom is natively integrated into the entire Primal stack and enabled by default. If you are using Primal 2.2 or later, you don't need to do anything to enable Blossom, all your media uploads are blossoming already.
To enhance user privacy, all Primal apps use the "/media" endpoint per BUD-05, which strips all metadata from uploaded files before they are saved and optionally mirrored to other Blossom servers, per user settings. You can use any Blossom server as your primary media server in Primal, as well as setup any number of mirrors:
 ## Conclusion
## ConclusionFor such a simple protocol, Blossom gives us three major benefits:
- Verifiable authenticity. All Nostr notes are always signed by the note author. With Blossom, the signed note includes a unique hash for each referenced media file, making it impossible to falsify.
- File hosting redundancy. Having multiple live copies of referenced media files (via Blossom mirroring) greatly increases the resiliency of media content published on Nostr.
- Censorship resistance. Blossom enables us to seamlessly switch media hosting providers in case of censorship.
Thanks for reading; and enjoy! 🌸
-
 @ 6e64b83c:94102ee8
2025-05-05 16:50:13
@ 6e64b83c:94102ee8
2025-05-05 16:50:13Nostr-static is a powerful static site generator that transforms long-form Nostr content into beautiful, standalone websites. It makes your content accessible to everyone, even those not using Nostr clients. For more information check out my previous blog post How to Create a Blog Out of Nostr Long-Form Articles
What's New in Version 0.7?
RSS and Atom Feeds
Version 0.7 brings comprehensive feed support with both RSS and Atom formats. The system automatically generates feeds for your main content, individual profiles, and tag-specific pages. These feeds are seamlessly integrated into your site's header, making them easily discoverable by feed readers and content aggregators.
This feature bridges the gap between Nostr and traditional web publishing, allowing your content to reach readers who prefer feed readers or automated content distribution systems.
Smart Content Discovery
The new tag discovery system enhances your readers' experience by automatically finding and recommending relevant articles from the Nostr network. It works by:
- Analyzing the tags in your articles
- Fetching popular articles from Nostr that share these tags
- Using configurable weights to rank these articles based on:
- Engagement metrics (reactions, reposts, replies)
- Zap statistics (amount, unique zappers, average zap size)
- Content quality signals (report penalties)
This creates a dynamic "Recommended Articles" section that helps readers discover more content they might be interested in, all while staying within the Nostr ecosystem.
See the new features yourself by visiting our demo at: https://blog.nostrize.me
-
 @ 6e0ea5d6:0327f353
2025-05-04 14:53:42
@ 6e0ea5d6:0327f353
2025-05-04 14:53:42Amico mio, ascolta bene!
Without hesitation, the woman you attract with lies is not truly yours. Davvero, she is the temporary property of the illusion you’ve built to seduce her. And every illusion, sooner or later, crumbles.
Weak men sell inflated versions of themselves. They talk about what they don’t have, promise what they can’t sustain, adorn their empty selves with words that are nothing more than a coat of paint. And they do this thinking that, later, they’ll be able to "show who they really are." Fatal mistake, cazzo!
The truth, amico mio, is not something that appears at the end. It is what holds up the whole beginning.
The woman who approaches a lie may smile at first — but she is smiling at the theater, not at the actor. When the curtains fall, what she will see is not a man. It will be a character tired of performing, begging for love from a self-serving audience in the front row.
That’s why I always point out that lying to win a woman’s heart is the same as sabotaging your own nature. The woman who comes through an invented version of you will be the first to leave when the veil of lies tears apart. Not out of cruelty, but out of consistency with her own interest. Fine... She didn’t leave you, but rather, that version of yourself never truly existed to be left behind.
A worthy man presents himself without deceptive adornments. And those who stay, stay because they know exactly who they are choosing as a man. That’s what differentiates forged seduction from the convenience of love built on honor, loyalty, and respect.
Ah, amico mio, I remember well. It was lunch on an autumn day in Catania. Mediterranean heat, and the Nero D'Avola wine from midday clinging to the lips like dried blood. Sitting in the shade of a lemon tree planted right by my grandfather's vineyard entrance, my uncle — the oldest of my father’s brothers — spoke little, but when he called us to sit by his side, all the nephews would quiet down to listen. And in my youth, he told me something that has never left my mind.
“In Sicily, the woman who endures the silence of a man about his business is more loyal than the one who is enchanted by speeches about what he does or how much he earns. Perchè, figlio mio, the first one has seen the truth. The second one, only a false shine.”
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 266815e0:6cd408a5
2025-05-02 22:24:59
@ 266815e0:6cd408a5
2025-05-02 22:24:59Its been six long months of refactoring code and building out to the applesauce packages but the app is stable enough for another release.
This update is pretty much a full rewrite of the non-visible parts of the app. all the background services were either moved out to the applesauce packages or rewritten, the result is that noStrudel is a little faster and much more consistent with connections and publishing.
New layout
The app has a new layout now, it takes advantage of the full desktop screen and looks a little better than it did before.
Removed NIP-72 communities
The NIP-72 communities are no longer part of the app, if you want to continue using them there are still a few apps that support them ( like satellite.earth ) but noStrudel won't support them going forward.
The communities where interesting but ultimately proved too have some fundamental flaws, most notably that all posts had to be approved by a moderator. There were some good ideas on how to improve it but they would have only been patches and wouldn't have fixed the underlying issues.
I wont promise to build it into noStrudel, but NIP-29 (relay based groups) look a lot more promising and already have better moderation abilities then NIP-72 communities could ever have.
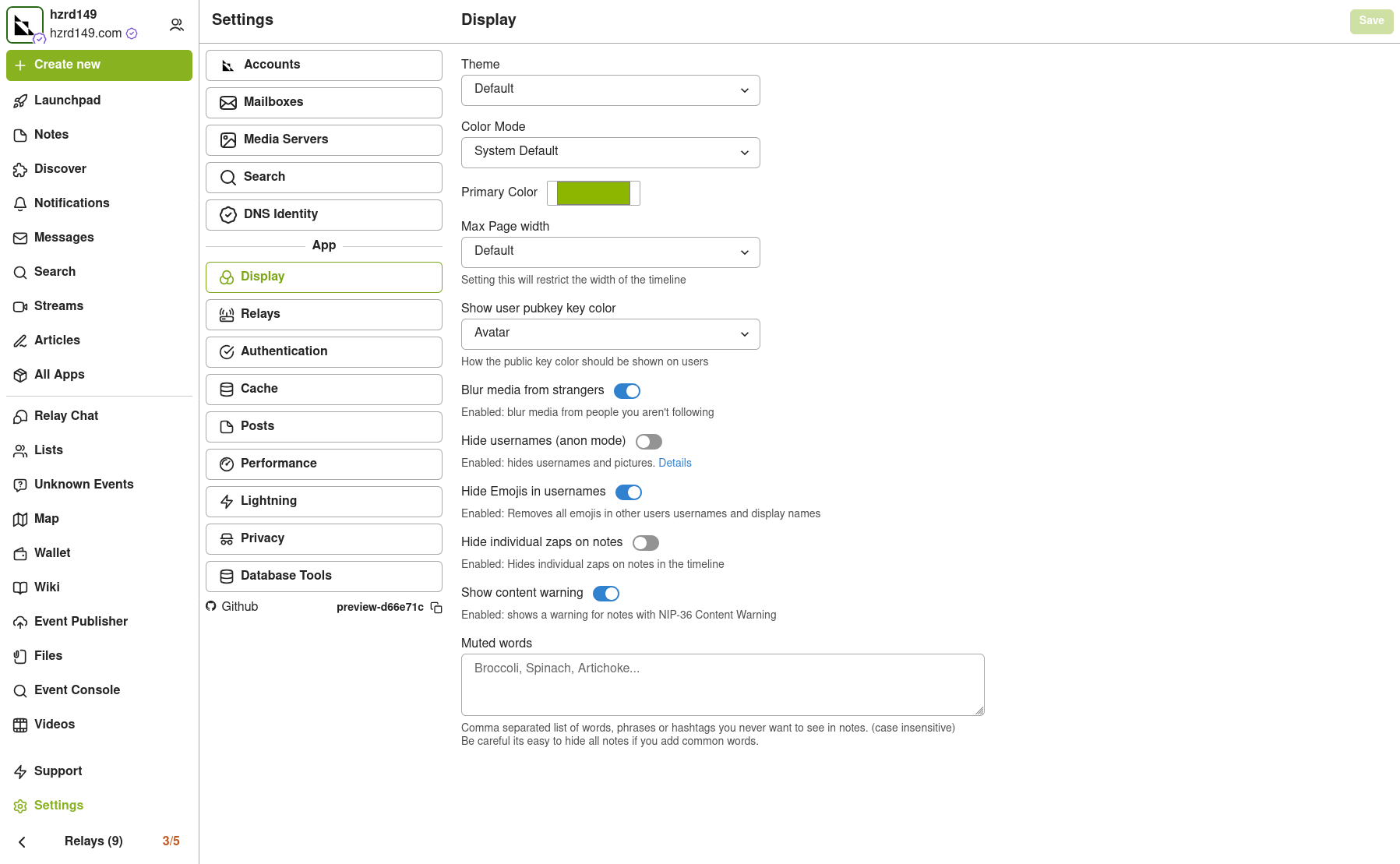
Settings view
There is now a dedicated settings view, so no more hunting around for where the relays are set or trying to find how to add another account. its all in one place now
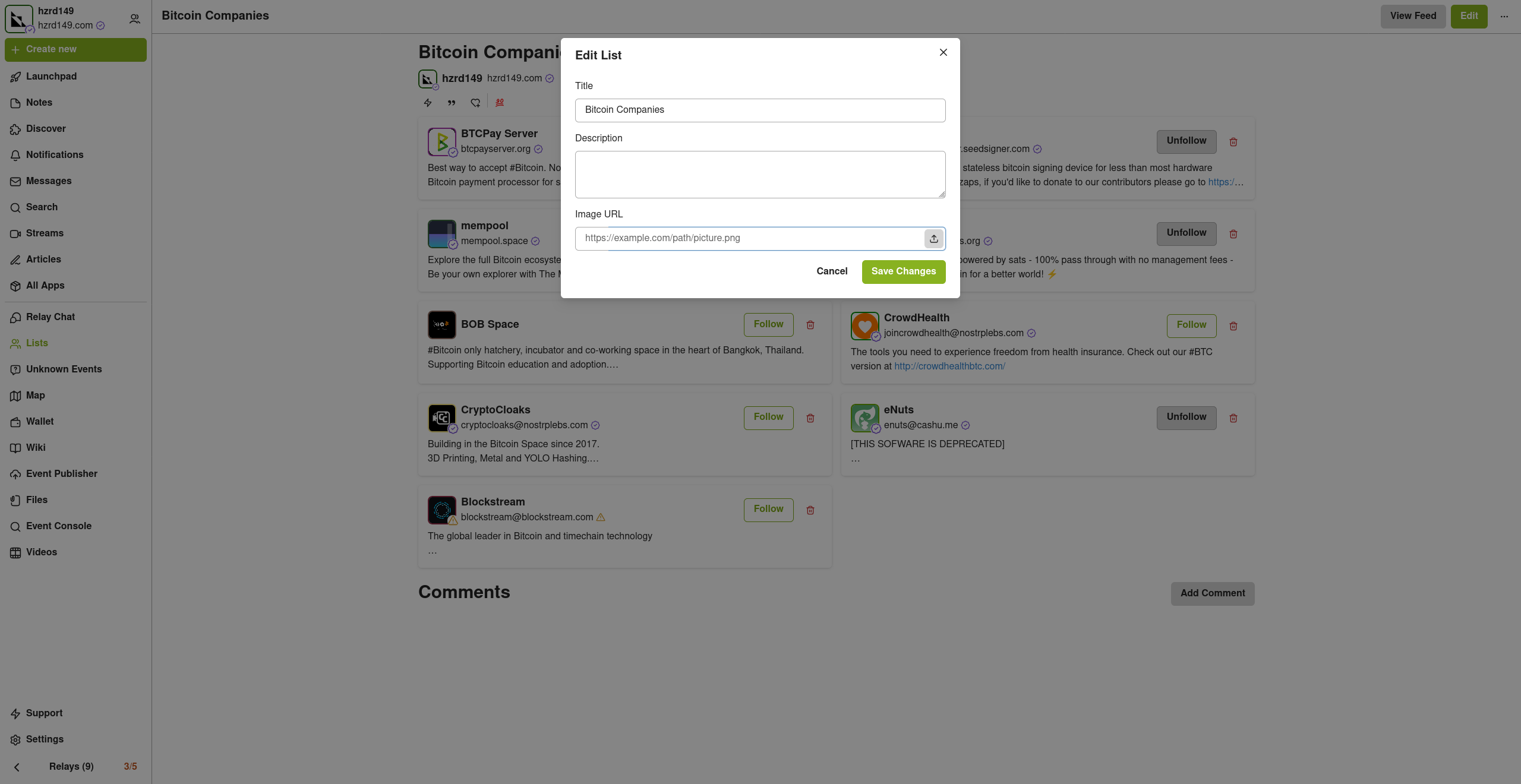
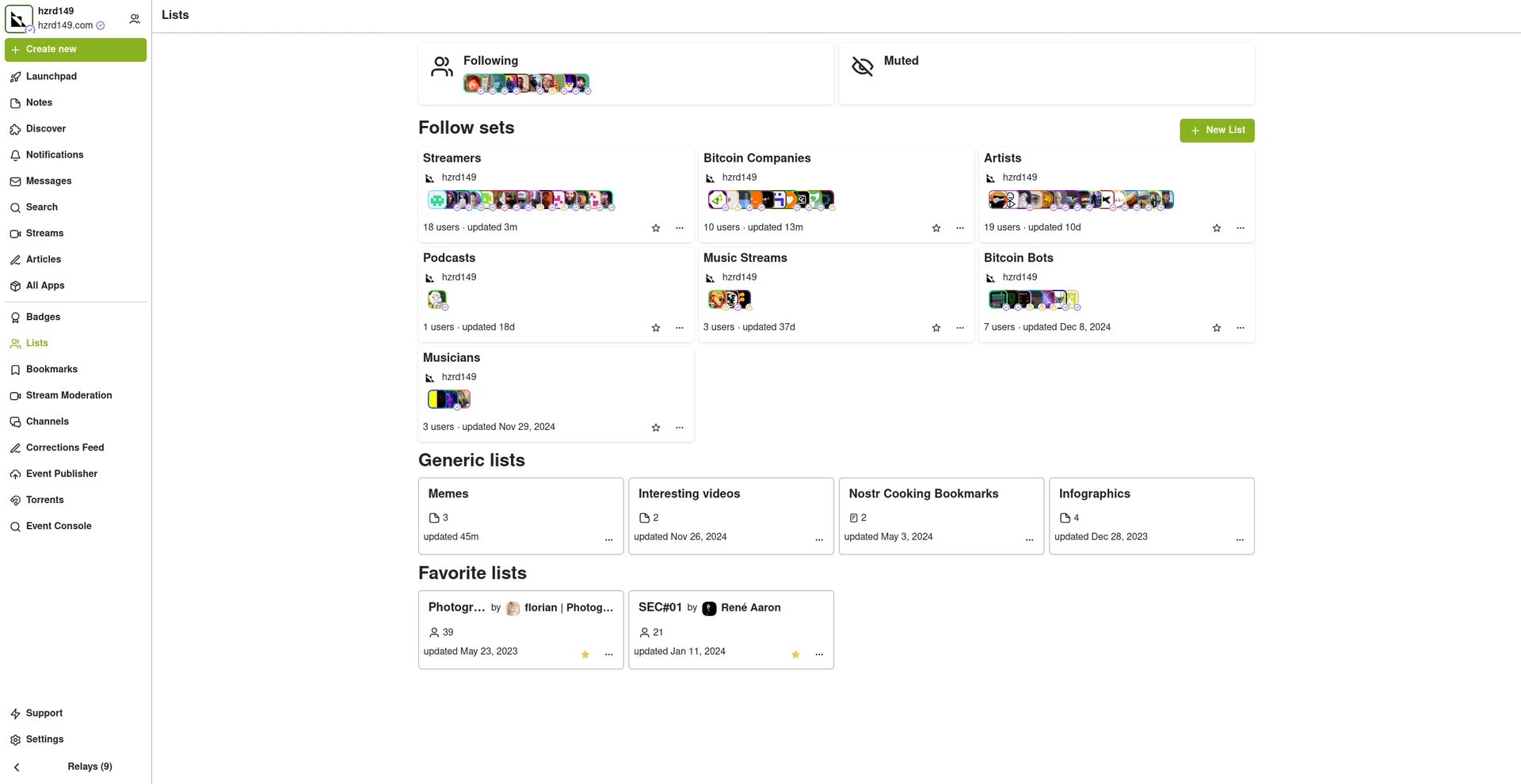
Cleaned up lists
The list views are a little cleaner now, and they have a simple edit modal
New emoji picker
Just another small improvement that makes the app feel more complete.
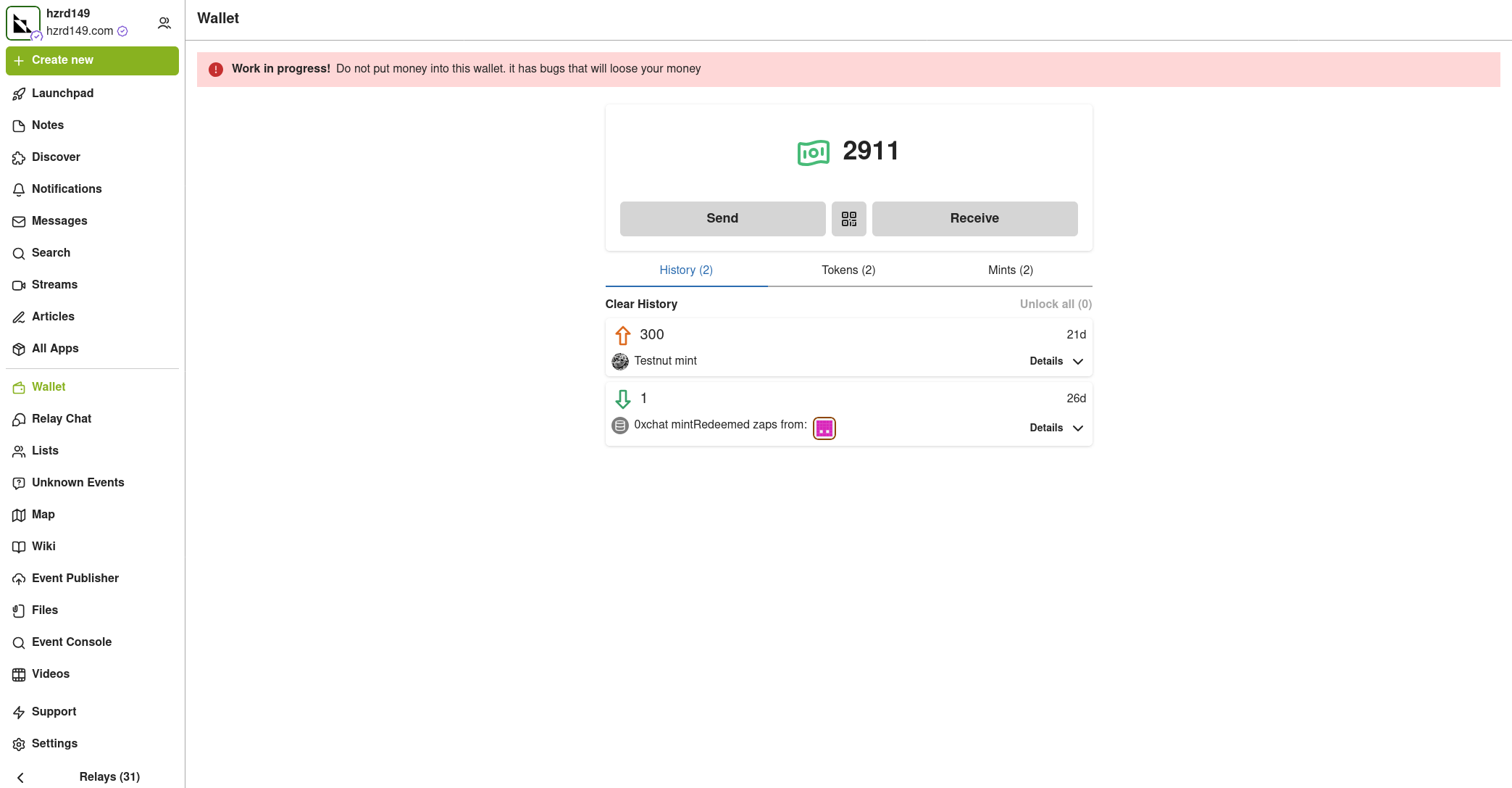
Experimental Wallet
There is a new "wallet" view in the app that lets you manage your NIP-60 cashu wallet. its very experimental and probably won't work for you, but its there and I hope to finish it up so the app can support NIP-61 nutzaps.
WARNING: Don't feed the wallet your hard earned sats, it will eat them!
Smaller improvements
- Added NSFW flag for replies
- Updated NIP-48 bunker login to work with new spec
- Linkfy BIPs
- Added 404 page
- Add NIP-22 comments under badges, files, and articles
- Add max height to timeline notes
- Fix articles view freezing on load
- Add option to mirror blobs when sharing notes
- Remove "open in drawer" for notes
-
 @ 088436cd:9d2646cc
2025-05-01 21:01:55
@ 088436cd:9d2646cc
2025-05-01 21:01:55The arrival of the coronavirus brought not only illness and death but also fear and panic. In such an environment of uncertainty, people have naturally stocked up on necessities, not knowing when things will return to normal.
Retail shelves have been cleared out, and even online suppliers like Amazon and Walmart are out of stock for some items. Independent sellers on these e-commerce platforms have had to fill the gap. With the huge increase in demand, they have found that their inventory has skyrocketed in value.
Many in need of these items (e.g. toilet paper, hand sanitizer and masks) balk at the new prices. They feel they are being taken advantage of in a time of need and call for intervention by the government to lower prices. The government has heeded that call, labeling the independent sellers as "price gougers" and threatening sanctions if they don't lower their prices. Amazon has suspended seller accounts and law enforcement at all levels have threatened to prosecute. Prices have dropped as a result and at first glance this seems like a victory for fair play. But, we will have to dig deeper to understand the unseen consequences of this intervention.
We must look at the economics of the situation, how supply and demand result in a price and how that price acts as a signal that goes out to everyone, informing them of underlying conditions in the economy and helping coordinate their actions.
It all started with a rise in demand. Given a fixed supply (e.g., the limited stock on shelves and in warehouses), an increase in demand inevitably leads to higher prices. Most people are familiar with this phenomenon, such as paying more for airline tickets during holidays or surge pricing for rides.
Higher prices discourage less critical uses of scarce resources. For example, you might not pay $1,000 for a plane ticket to visit your aunt if you can get one for $100 the following week, but someone else might pay that price to visit a dying relative. They value that plane seat more than you.
*** During the crisis, demand surged and their shelves emptied even though
However, retail outlets have not raised prices. They have kept them low, so the low-value uses of things like toilet paper, masks and hand sanitizer has continued. Often, this "use" just takes the form of hoarding. At everyday low prices, it makes sense to buy hundreds of rolls and bottles. You know you will use them eventually, so why not stock up? And, with all those extra supplies in the closet and basement, you don't need to change your behavior much. You don't have to ration your use.
At the low prices, these scarce resources got bought up faster and faster until there was simply none left. The reality of the situation became painfully clear to those who didn't panic and got to the store late: You have no toilet paper and you're not going to any time soon.
However, if prices had been allowed to rise, a number of effects would have taken place that would have coordinated the behavior of everyone so that valuable resources would not have been wasted or hoarded, and everyone could have had access to what they needed.
On the demand side, if prices had been allowed to rise, people would have begun to self-ration. You might leave those extra plies on the roll next time if you know they will cost ten times as much to replace. Or, you might choose to clean up a spill with a rag rather than disposable tissue. Most importantly, you won't hoard as much. That 50th bottle of hand sanitizer might just not be worth it at the new, high price. You'll leave it on the shelf for someone else who may have none.
On the supply side, higher prices would have incentivized people to offer up more of their stockpiles for sale. If you have a pallet full of toilet paper in your basement and all of the sudden they are worth $15 per roll, you might just list a few online. But, if it is illegal to do so, you probably won't.
Imagine you run a business installing insulation and have a few thousand respirator masks on hand for your employees. During a pandemic, it is much more important that people breathe filtered air than that insulation get installed, and that fact is reflected in higher prices. You will sell your extra masks at the higher price rather than store them for future insulation jobs, and the scarce resource will be put to its most important use.
Producers of hand sanitizer would go into overdrive if prices were allowed to rise. They would pay their employees overtime, hire new ones, and pay a premium for their supplies, making sure their raw materials don't go to less important uses.
These kinds of coordinated actions all across the economy would be impossible without real prices to guide them. How do you know if it makes sense to spend an extra $10k bringing a thousand masks to market unless you know you can get more than $10 per mask? If the price is kept artificially low, you simply can't do it. The money just isn't there.
These are the immediate effects of a price change, but incredibly, price changes also coordinate people's actions across space and time.
Across space, there are different supply and demand conditions in different places, and thus prices are not uniform. We know some places are real "hot spots" for the virus, while others are mostly unaffected. High demand in the hot spots leads to higher prices there, which attracts more of the resource to those areas. Boxes and boxes of essential items would pour in where they are needed most from where they are needed least, but only if prices were allowed to adjust freely.
This would be accomplished by individuals and businesses buying low in the unaffected areas, selling high in the hot spots and subtracting their labor and transportation costs from the difference. Producers of new supply would know exactly where it is most needed and ship to the high-demand, high-price areas first. The effect of these actions is to increase prices in the low demand areas and reduce them in the high demand areas. People in the low demand areas will start to self-ration more, reflecting the reality of their neighbors, and people in the hotspots will get some relief.
However, by artificially suppressing prices in the hot spot, people there will simply buy up the available supply and run out, and it will be cost prohibitive to bring in new supply from low-demand areas.
Prices coordinate economic actions across time as well. Just as entrepreneurs and businesses can profit by transporting scarce necessities from low-demand to high-demand areas, they can also profit by buying in low-demand times and storing their merchandise for when it is needed most.
Just as allowing prices to freely adjust in one area relative to another will send all the right signals for the optimal use of a scarce resource, allowing prices to freely adjust over time will do the same.
When an entrepreneur buys up resources during low-demand times in anticipation of a crisis, she restricts supply ahead of the crisis, which leads to a price increase. She effectively bids up the price. The change in price affects consumers and producers in all the ways mentioned above. Consumers self-ration more, and producers bring more of the resource to market.
Our entrepreneur has done a truly incredible thing. She has predicted the future, and by so doing has caused every individual in the economy to prepare for a shortage they don't even know is coming! And, by discouraging consumption and encouraging production ahead of time, she blunts the impact the crisis will have. There will be more of the resource to go around when it is needed most.
On top of this, our entrepreneur still has her stockpile she saved back when everyone else was blithely using it up. She can now further mitigate the damage of the crisis by selling her stock during the worst of it, when people are most desperate for relief. She will know when this is because the price will tell her, but only if it is allowed to adjust freely. When the price is at its highest is when people need the resource the most, and those willing to pay will not waste it or hoard it. They will put it to its highest valued use.
The economy is like a big bus we are all riding in, going down a road with many twists and turns. Just as it is difficult to see into the future, it is difficult to see out the bus windows at the road ahead.
On the dashboard, we don't have a speedometer or fuel gauge. Instead we have all the prices for everything in the economy. Prices are what tell us the condition of the bus and the road. They tell us everything. Without them, we are blind.
Good times are a smooth road. Consumer prices and interest rates are low, investment returns are steady. We hit the gas and go fast. But, the road is not always straight and smooth. Sometimes there are sharp turns and rough patches. Successful entrepreneurs are the ones who can see what is coming better than everyone else. They are our navigators.
When they buy up scarce resources ahead of a crisis, they are hitting the brakes and slowing us down. When they divert resources from one area to another, they are steering us onto a smoother path. By their actions in the market, they adjust the prices on our dashboard to reflect the conditions of the road ahead, so we can prepare for, navigate and get through the inevitable difficulties we will face.
Interfering with the dashboard by imposing price floors or price caps doesn't change the conditions of the road (the number of toilet paper rolls in existence hasn't changed). All it does is distort our perception of those conditions. We think the road is still smooth--our heavy foot stomping the gas--as we crash onto a rocky dirt road at 80 miles per hour (empty shelves at the store for weeks on end).
Supply, demand and prices are laws of nature. All of this is just how things work. It isn't right or wrong in a moral sense. Price caps lead to waste, shortages and hoarding as surely as water flows downhill. The opposite--allowing prices to adjust freely--leads to conservation of scarce resources and their being put to their highest valued use. And yes, it leads to profits for the entrepreneurs who were able to correctly predict future conditions, and losses for those who weren't.
Is it fair that they should collect these profits? On the one hand, anyone could have stocked up on toilet paper, hand sanitizer and face masks at any time before the crisis, so we all had a fair chance to get the supplies cheaply. On the other hand, it just feels wrong that some should profit so much at a time when there is so much need.
Our instinct in the moment is to see the entrepreneur as a villain, greedy "price gouger". But we don't see the long chain of economic consequences the led to the situation we feel is unfair.
If it weren't for anti-price-gouging laws, the major retailers would have raised their prices long before the crisis became acute. When they saw demand outstrip supply, they would have raised prices, not by 100 fold, but gradually and long before anyone knew how serious things would have become. Late comers would have had to pay more, but at least there would be something left on the shelf.
As an entrepreneur, why take risks trying to anticipate the future if you can't reap the reward when you are right? Instead of letting instead of letting entrepreneurs--our navigators--guide us, we are punishing and vilifying them, trying to force prices to reflect a reality that simply doesn't exist.
In a crisis, more than any other time, prices must be allowed to fluctuate. To do otherwise is to blind ourselves at a time when danger and uncertainty abound. It is economic suicide.
In a crisis, there is great need, and the way to meet that need is not by pretending it's not there, by forcing prices to reflect a world where there isn't need. They way to meet the need is the same it has always been, through charity.
If the people in government want to help, the best way for the to do so is to be charitable and reduce their taxes and fees as much as possible, ideally to zero in a time of crisis. Amazon, for example, could instantly reduce the price of all crisis related necessities by 20% if they waived their fee. This would allow for more uses by more people of these scarce supplies as hoarders release their stockpiles on to the market, knowing they can get 20% more for their stock. Governments could reduce or eliminate their tax burden on high-demand, crisis-related items and all the factors that go into their production, with the same effect: a reduction in prices and expansion of supply. All of us, including the successful entrepreneurs and the wealthy for whom high prices are not a great burden, could donate to relief efforts.
These ideas are not new or untested. This is core micro economics. It has been taught for hundreds of years in universities the world over. The fact that every crisis that comes along stirs up ire against entrepreneurs indicates not that the economics is wrong, but that we have a strong visceral reaction against what we perceive to be unfairness. This is as it should be. Unfairness is wrong and the anger it stirs in us should compel us to right the wrong. Our anger itself isn't wrong, it's just misplaced.
Entrepreneurs didn't cause the prices to rise. Our reaction to a virus did that. We saw a serious threat and an uncertain future and followed our natural impulse to hoard. Because prices at major retail suppliers didn't rise, that impulse ran rampant and we cleared the shelves until there was nothing left. We ran the bus right off the road and them blamed the entrepreneurs for showing us the reality of our situation, for shaking us out of the fantasy of low prices.
All of this is not to say that entrepreneurs are high-minded public servants. They are just doing their job. Staking your money on an uncertain future is a risky business. There are big risks and big rewards. Most entrepreneurs just scrape by or lose their capital in failed ventures.
However, the ones that get it right must be allowed to keep their profits, or else no one will try and we'll all be driving blind. We need our navigators. It doesn't even matter if they know all the positive effects they are having on the rest of us and the economy as a whole. So long as they are buying low and selling high--so long as they are doing their job--they will be guiding the rest of us through the good times and the bad, down the open road and through the rough spots.
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ a008def1:57a3564d
2025-04-30 17:52:11
@ a008def1:57a3564d
2025-04-30 17:52:11A Vision for #GitViaNostr
Git has long been the standard for version control in software development, but over time, we has lost its distributed nature. Originally, Git used open, permissionless email for collaboration, which worked well at scale. However, the rise of GitHub and its centralized pull request (PR) model has shifted the landscape.
Now, we have the opportunity to revive Git's permissionless and distributed nature through Nostr!
We’ve developed tools to facilitate Git collaboration via Nostr, but there are still significant friction that prevents widespread adoption. This article outlines a vision for how we can reduce those barriers and encourage more repositories to embrace this approach.
First, we’ll review our progress so far. Then, we’ll propose a guiding philosophy for our next steps. Finally, we’ll discuss a vision to tackle specific challenges, mainly relating to the role of the Git server and CI/CD.
I am the lead maintainer of ngit and gitworkshop.dev, and I’ve been fortunate to work full-time on this initiative for the past two years, thanks to an OpenSats grant.
How Far We’ve Come
The aim of #GitViaNostr is to liberate discussions around code collaboration from permissioned walled gardens. At the core of this collaboration is the process of proposing and applying changes. That's what we focused on first.
Since Nostr shares characteristics with email, and with NIP34, we’ve adopted similar primitives to those used in the patches-over-email workflow. This is because of their simplicity and that they don’t require contributors to host anything, which adds reliability and makes participation more accessible.
However, the fork-branch-PR-merge workflow is the only model many developers have known, and changing established workflows can be challenging. To address this, we developed a new workflow that balances familiarity, user experience, and alignment with the Nostr protocol: the branch-PR-merge model.
This model is implemented in ngit, which includes a Git plugin that allows users to engage without needing to learn new commands. Additionally, gitworkshop.dev offers a GitHub-like interface for interacting with PRs and issues. We encourage you to try them out using the quick start guide and share your feedback. You can also explore PRs and issues with gitplaza.
For those who prefer the patches-over-email workflow, you can still use that approach with Nostr through gitstr or the
ngit sendandngit listcommands, and explore patches with patch34.The tools are now available to support the core collaboration challenge, but we are still at the beginning of the adoption curve.
Before we dive into the challenges—such as why the Git server setup can be jarring and the possibilities surrounding CI/CD—let’s take a moment to reflect on how we should approach the challenges ahead of us.
Philosophy
Here are some foundational principles I shared a few years ago:
- Let Git be Git
- Let Nostr be Nostr
- Learn from the successes of others
I’d like to add one more:
- Embrace anarchy and resist monolithic development.
Micro Clients FTW
Nostr celebrates simplicity, and we should strive to maintain that. Monolithic developments often lead to unnecessary complexity. Projects like gitworkshop.dev, which aim to cover various aspects of the code collaboration experience, should not stifle innovation.
Just yesterday, the launch of following.space demonstrated how vibe-coded micro clients can make a significant impact. They can be valuable on their own, shape the ecosystem, and help push large and widely used clients to implement features and ideas.
The primitives in NIP34 are straightforward, and if there are any barriers preventing the vibe-coding of a #GitViaNostr app in an afternoon, we should work to eliminate them.
Micro clients should lead the way and explore new workflows, experiences, and models of thinking.
Take kanbanstr.com. It provides excellent project management and organization features that work seamlessly with NIP34 primitives.
From kanban to code snippets, from CI/CD runners to SatShoot—may a thousand flowers bloom, and a thousand more after them.
Friction and Challenges
The Git Server
In #GitViaNostr, maintainers' branches (e.g.,
master) are hosted on a Git server. Here’s why this approach is beneficial:- Follows the original Git vision and the "let Git be Git" philosophy.
- Super efficient, battle-tested, and compatible with all the ways people use Git (e.g., LFS, shallow cloning).
- Maintains compatibility with related systems without the need for plugins (e.g., for build and deployment).
- Only repository maintainers need write access.
In the original Git model, all users would need to add the Git server as a 'git remote.' However, with ngit, the Git server is hidden behind a Nostr remote, which enables:
- Hiding complexity from contributors and users, so that only maintainers need to know about the Git server component to start using #GitViaNostr.
- Maintainers can easily swap Git servers by updating their announcement event, allowing contributors/users using ngit to automatically switch to the new one.
Challenges with the Git Server
While the Git server model has its advantages, it also presents several challenges:
- Initial Setup: When creating a new repository, maintainers must select a Git server, which can be a jarring experience. Most options come with bloated social collaboration features tied to a centralized PR model, often difficult or impossible to disable.
-
Manual Configuration: New repositories require manual configuration, including adding new maintainers through a browser UI, which can be cumbersome and time-consuming.
-
User Onboarding: Many Git servers require email sign-up or KYC (Know Your Customer) processes, which can be a significant turn-off for new users exploring a decentralized and permissionless alternative to GitHub.
Once the initial setup is complete, the system works well if a reliable Git server is chosen. However, this is a significant "if," as we have become accustomed to the excellent uptime and reliability of GitHub. Even professionally run alternatives like Codeberg can experience downtime, which is frustrating when CI/CD and deployment processes are affected. This problem is exacerbated when self-hosting.
Currently, most repositories on Nostr rely on GitHub as the Git server. While maintainers can change servers without disrupting their contributors, this reliance on a centralized service is not the decentralized dream we aspire to achieve.
Vision for the Git Server
The goal is to transform the Git server from a single point of truth and failure into a component similar to a Nostr relay.
Functionality Already in ngit to Support This
-
State on Nostr: Store the state of branches and tags in a Nostr event, removing reliance on a single server. This validates that the data received has been signed by the maintainer, significantly reducing the trust requirement.
-
Proxy to Multiple Git Servers: Proxy requests to all servers listed in the announcement event, adding redundancy and eliminating the need for any one server to match GitHub's reliability.
Implementation Requirements
To achieve this vision, the Nostr Git server implementation should:
-
Implement the Git Smart HTTP Protocol without authentication (no SSH) and only accept pushes if the reference tip matches the latest state event.
-
Avoid Bloat: There should be no user authentication, no database, no web UI, and no unnecessary features.
-
Automatic Repository Management: Accept or reject new repositories automatically upon the first push based on the content of the repository announcement event referenced in the URL path and its author.
Just as there are many free, paid, and self-hosted relays, there will be a variety of free, zero-step signup options, as well as self-hosted and paid solutions.
Some servers may use a Web of Trust (WoT) to filter out spam, while others might impose bandwidth or repository size limits for free tiers or whitelist specific npubs.
Additionally, some implementations could bundle relay and blossom server functionalities to unify the provision of repository data into a single service. These would likely only accept content related to the stored repositories rather than general social nostr content.
The potential role of CI / CD via nostr DVMs could create the incentives for a market of highly reliable free at the point of use git servers.
This could make onboarding #GitViaNostr repositories as easy as entering a name and selecting from a multi-select list of Git server providers that announce via NIP89.
!(image)[https://image.nostr.build/badedc822995eb18b6d3c4bff0743b12b2e5ac018845ba498ce4aab0727caf6c.jpg]
Git Client in the Browser
Currently, many tasks are performed on a Git server web UI, such as:
- Browsing code, commits, branches, tags, etc.
- Creating and displaying permalinks to specific lines in commits.
- Merging PRs.
- Making small commits and PRs on-the-fly.
Just as nobody goes to the web UI of a relay (e.g., nos.lol) to interact with notes, nobody should need to go to a Git server to interact with repositories. We use the Nostr protocol to interact with Nostr relays, and we should use the Git protocol to interact with Git servers. This situation has evolved due to the centralization of Git servers. Instead of being restricted to the view and experience designed by the server operator, users should be able to choose the user experience that works best for them from a range of clients. To facilitate this, we need a library that lowers the barrier to entry for creating these experiences. This library should not require a full clone of every repository and should not depend on proprietary APIs. As a starting point, I propose wrapping the WASM-compiled gitlib2 library for the web and creating useful functions, such as showing a file, which utilizes clever flags to minimize bandwidth usage (e.g., shallow clone, noblob, etc.).
This approach would not only enhance clients like gitworkshop.dev but also bring forth a vision where Git servers simply run the Git protocol, making vibe coding Git experiences even better.
song
nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 created song with a complementary vision that has shaped how I see the role of the git server. Its a self-hosted, nostr-permissioned git server with a relay baked in. Its currently a WIP and there are some compatability with ngit that we need to work out.
We collaborated on the nostr-permissioning approach now reflected in nip34.
I'm really excited to see how this space evolves.
CI/CD
Most projects require CI/CD, and while this is often bundled with Git hosting solutions, it is currently not smoothly integrated into #GitViaNostr yet. There are many loosely coupled options, such as Jenkins, Travis, CircleCI, etc., that could be integrated with Nostr.
However, the more exciting prospect is to use DVMs (Data Vending Machines).
DVMs for CI/CD
Nostr Data Vending Machines (DVMs) can provide a marketplace of CI/CD task runners with Cashu for micro payments.
There are various trust levels in CI/CD tasks:
- Tasks with no secrets eg. tests.
- Tasks using updatable secrets eg. API keys.
- Unverifiable builds and steps that sign with Android, Nostr, or PGP keys.
DVMs allow tasks to be kicked off with specific providers using a Cashu token as payment.
It might be suitable for some high-compute and easily verifiable tasks to be run by the cheapest available providers. Medium trust tasks could be run by providers with a good reputation, while high trust tasks could be run on self-hosted runners.
Job requests, status, and results all get published to Nostr for display in Git-focused Nostr clients.
Jobs could be triggered manually, or self-hosted runners could be configured to watch a Nostr repository and kick off jobs using their own runners without payment.
But I'm most excited about the prospect of Watcher Agents.
CI/CD Watcher Agents
AI agents empowered with a NIP60 Cashu wallet can run tasks based on activity, such as a push to master or a new PR, using the most suitable available DVM runner that meets the user's criteria. To keep them running, anyone could top up their NIP60 Cashu wallet; otherwise, the watcher turns off when the funds run out. It could be users, maintainers, or anyone interested in helping the project who could top up the Watcher Agent's balance.
As aluded to earlier, part of building a reputation as a CI/CD provider could involve running reliable hosting (Git server, relay, and blossom server) for all FOSS Nostr Git repositories.
This provides a sustainable revenue model for hosting providers and creates incentives for many free-at-the-point-of-use hosting providers. This, in turn, would allow one-click Nostr repository creation workflows, instantly hosted by many different providers.
Progress to Date
nostr:npub1hw6amg8p24ne08c9gdq8hhpqx0t0pwanpae9z25crn7m9uy7yarse465gr and nostr:npub16ux4qzg4qjue95vr3q327fzata4n594c9kgh4jmeyn80v8k54nhqg6lra7 have been working on a runner that uses GitHub Actions YAML syntax (using act) for the dvm-cicd-runner and takes Cashu payment. You can see example runs on GitWorkshop. It currently takes testnuts, doesn't give any change, and the schema will likely change.
Note: The actions tab on GitWorkshop is currently available on all repositories if you turn on experimental mode (under settings in the user menu).
It's a work in progress, and we expect the format and schema to evolve.
Easy Web App Deployment
For those disapointed not to find a 'Nostr' button to import a git repository to Vercel menu: take heart, they made it easy. vercel.com_import_options.png there is a vercel cli that can be easily called in CI / CD jobs to kick of deployments. Not all managed solutions for web app deployment (eg. netlify) make it that easy.
Many More Opportunities
Large Patches via Blossom
I would be remiss not to mention the large patch problem. Some patches are too big to fit into Nostr events. Blossom is perfect for this, as it allows these larger patches to be included in a blossom file and referenced in a new patch kind.
Enhancing the #GitViaNostr Experience
Beyond the large patch issue, there are numerous opportunities to enhance the #GitViaNostr ecosystem. We can focus on improving browsing, discovery, social and notifications. Receiving notifications on daily driver Nostr apps is one of the killer features of Nostr. However, we must ensure that Git-related notifications are easily reviewable, so we don’t miss any critical updates.
We need to develop tools that cater to our curiosity—tools that enable us to discover and follow projects, engage in discussions that pique our interest, and stay informed about developments relevant to our work.
Additionally, we should not overlook the importance of robust search capabilities and tools that facilitate migrations.
Concluding Thoughts
The design space is vast. Its an exciting time to be working on freedom tech. I encourage everyone to contribute their ideas and creativity and get vibe-coding!
I welcome your honest feedback on this vision and any suggestions you might have. Your insights are invaluable as we collaborate to shape the future of #GitViaNostr. Onward.
Contributions
To conclude, I want to acknowledge some the individuals who have made recent code contributions related to #GitViaNostr:
nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 (gitstr, song, patch34), nostr:npub1useke4f9maul5nf67dj0m9sq6jcsmnjzzk4ycvldwl4qss35fvgqjdk5ks (gitplaza)
nostr:npub1elta7cneng3w8p9y4dw633qzdjr4kyvaparuyuttyrx6e8xp7xnq32cume (ngit contributions, git-remote-blossom),nostr:npub16p8v7varqwjes5hak6q7mz6pygqm4pwc6gve4mrned3xs8tz42gq7kfhdw (SatShoot, Flotilla-Budabit), nostr:npub1ehhfg09mr8z34wz85ek46a6rww4f7c7jsujxhdvmpqnl5hnrwsqq2szjqv (Flotilla-Budabit, Nostr Git Extension), nostr:npub1ahaz04ya9tehace3uy39hdhdryfvdkve9qdndkqp3tvehs6h8s5slq45hy (gnostr and experiments), and others.
nostr:npub1uplxcy63up7gx7cladkrvfqh834n7ylyp46l3e8t660l7peec8rsd2sfek (git-remote-nostr)
Project Management nostr:npub1ltx67888tz7lqnxlrg06x234vjnq349tcfyp52r0lstclp548mcqnuz40t (kanbanstr) Code Snippets nostr:npub1ygzj9skr9val9yqxkf67yf9jshtyhvvl0x76jp5er09nsc0p3j6qr260k2 (nodebin.io) nostr:npub1r0rs5q2gk0e3dk3nlc7gnu378ec6cnlenqp8a3cjhyzu6f8k5sgs4sq9ac (snipsnip.dev)
CI / CD nostr:npub16ux4qzg4qjue95vr3q327fzata4n594c9kgh4jmeyn80v8k54nhqg6lra7 nostr:npub1hw6amg8p24ne08c9gdq8hhpqx0t0pwanpae9z25crn7m9uy7yarse465gr
and for their nostr:npub1c03rad0r6q833vh57kyd3ndu2jry30nkr0wepqfpsm05vq7he25slryrnw nostr:npub1qqqqqq2stely3ynsgm5mh2nj3v0nk5gjyl3zqrzh34hxhvx806usxmln03 and nostr:npub1l5sga6xg72phsz5422ykujprejwud075ggrr3z2hwyrfgr7eylqstegx9z for their testing, feedback, ideas and encouragement.
Thank you for your support and collaboration! Let me know if I've missed you.
-
 @ 6be5cc06:5259daf0
2025-04-28 01:05:49
@ 6be5cc06:5259daf0
2025-04-28 01:05:49Eu reconheço que Deus, e somente Deus, é o soberano legítimo sobre todas as coisas. Nenhum homem, nenhuma instituição, nenhum parlamento tem autoridade para usurpar aquilo que pertence ao Rei dos reis. O Estado moderno, com sua pretensão totalizante, é uma farsa blasfema diante do trono de Cristo. Não aceito outro senhor.
A Lei que me guia não é a ditada por burocratas, mas a gravada por Deus na própria natureza humana. A razão, quando iluminada pela fé, é suficiente para discernir o que é justo. Rejeito as leis arbitrárias que pretendem legitimar o roubo, o assassinato ou a escravidão em nome da ordem. A justiça não nasce do decreto, mas da verdade.
Acredito firmemente na propriedade privada como extensão da própria pessoa. Aquilo que é fruto do meu trabalho, da minha criatividade, da minha dedicação, dos dons a mim concedidos por Deus, pertence a mim por direito natural. Ninguém pode legitimamente tomar o que é meu sem meu consentimento. Todo imposto é uma agressão; toda expropriação, um roubo. Defendo a liberdade econômica não por idolatria ao mercado, mas porque a liberdade é condição necessária para a virtude.
Assumo o Princípio da Não Agressão como o mínimo ético que devo respeitar. Não iniciarei o uso da força contra ninguém, nem contra sua propriedade. Exijo o mesmo de todos. Mas sei que isso não basta. O PNA delimita o que não devo fazer — ele não me ensina o que devo ser. A liberdade exterior só é boa se houver liberdade interior. O mercado pode ser livre, mas se a alma estiver escravizada pelo vício, o colapso será inevitável.
Por isso, não me basta a ética negativa. Creio que uma sociedade justa precisa de valores positivos: honra, responsabilidade, compaixão, respeito, fidelidade à verdade. Sem isso, mesmo uma sociedade que respeite formalmente os direitos individuais apodrecerá por dentro. Um povo que ama o lucro, mas despreza a verdade, que celebra a liberdade mas esquece a justiça, está se preparando para ser dominado. Trocará um déspota visível por mil tiranias invisíveis — o hedonismo, o consumismo, a mentira, o medo.
Não aceito a falsa caridade feita com o dinheiro tomado à força. A verdadeira generosidade nasce do coração livre, não da coerção institucional. Obrigar alguém a ajudar o próximo destrói tanto a liberdade quanto a virtude. Só há mérito onde há escolha. A caridade que nasce do amor é redentora; a que nasce do fisco é propaganda.
O Estado moderno é um ídolo. Ele promete segurança, mas entrega servidão. Promete justiça, mas entrega privilégios. Disfarça a opressão com linguagem técnica, legal e democrática. Mas por trás de suas máscaras, vejo apenas a velha serpente. Um parasita que se alimenta do trabalho alheio e manipula consciências para se perpetuar.
Resistir não é apenas um direito, é um dever. Obedecer a Deus antes que aos homens — essa é a minha regra. O poder se volta contra a verdade, mas minha lealdade pertence a quem criou o céu e a terra. A tirania não se combate com outro tirano, mas com a desobediência firme e pacífica dos que amam a justiça.
Não acredito em utopias. Desejo uma ordem natural, orgânica, enraizada no voluntarismo. Uma sociedade que se construa de baixo para cima: a partir da família, da comunidade local, da tradição e da fé. Não quero uma máquina que planeje a vida alheia, mas um tecido de relações voluntárias onde a liberdade floresça à sombra da cruz.
Desejo, sim, o reinado social de Cristo. Não por imposição, mas por convicção. Que Ele reine nos corações, nas famílias, nas ruas e nos contratos. Que a fé guie a razão e a razão ilumine a vida. Que a liberdade seja meio para a santidade — não um fim em si. E que, livres do jugo do Leviatã, sejamos servos apenas do Senhor.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ 30ceb64e:7f08bdf5
2025-04-26 20:33:30
@ 30ceb64e:7f08bdf5
2025-04-26 20:33:30Status: Draft
Author: TheWildHustleAbstract
This NIP defines a framework for storing and sharing health and fitness profile data on Nostr. It establishes a set of standardized event kinds for individual health metrics, allowing applications to selectively access specific health information while preserving user control and privacy.
In this framework exists - NIP-101h.1 Weight using kind 1351 - NIP-101h.2 Height using kind 1352 - NIP-101h.3 Age using kind 1353 - NIP-101h.4 Gender using kind 1354 - NIP-101h.5 Fitness Level using kind 1355
Motivation
I want to build and support an ecosystem of health and fitness related nostr clients that have the ability to share and utilize a bunch of specific interoperable health metrics.
- Selective access - Applications can access only the data they need
- User control - Users can choose which metrics to share
- Interoperability - Different health applications can share data
- Privacy - Sensitive health information can be managed independently
Specification
Kind Number Range
Health profile metrics use the kind number range 1351-1399:
| Kind | Metric | | --------- | ---------------------------------- | | 1351 | Weight | | 1352 | Height | | 1353 | Age | | 1354 | Gender | | 1355 | Fitness Level | | 1356-1399 | Reserved for future health metrics |
Common Structure
All health metric events SHOULD follow these guidelines:
- The content field contains the primary value of the metric
- Required tags:
['t', 'health']- For categorizing as health data['t', metric-specific-tag]- For identifying the specific metric['unit', unit-of-measurement]- When applicable- Optional tags:
['converted_value', value, unit]- For providing alternative unit measurements['timestamp', ISO8601-date]- When the metric was measured['source', application-name]- The source of the measurement
Unit Handling
Health metrics often have multiple ways to be measured. To ensure interoperability:
- Where multiple units are possible, one standard unit SHOULD be chosen as canonical
- When using non-standard units, a
converted_valuetag SHOULD be included with the canonical unit - Both the original and converted values should be provided for maximum compatibility
Client Implementation Guidelines
Clients implementing this NIP SHOULD:
- Allow users to explicitly choose which metrics to publish
- Support reading health metrics from other users when appropriate permissions exist
- Support updating metrics with new values over time
- Preserve tags they don't understand for future compatibility
- Support at least the canonical unit for each metric
Extensions
New health metrics can be proposed as extensions to this NIP using the format:
- NIP-101h.X where X is the metric number
Each extension MUST specify: - A unique kind number in the range 1351-1399 - The content format and meaning - Required and optional tags - Examples of valid events
Privacy Considerations
Health data is sensitive personal information. Clients implementing this NIP SHOULD:
- Make it clear to users when health data is being published
- Consider incorporating NIP-44 encryption for sensitive metrics
- Allow users to selectively share metrics with specific individuals
- Provide easy ways to delete previously published health data
NIP-101h.1: Weight
Description
This NIP defines the format for storing and sharing weight data on Nostr.
Event Kind: 1351
Content
The content field MUST contain the numeric weight value as a string.
Required Tags
- ['unit', 'kg' or 'lb'] - Unit of measurement
- ['t', 'health'] - Categorization tag
- ['t', 'weight'] - Specific metric tag
Optional Tags
- ['converted_value', value, unit] - Provides the weight in alternative units for interoperability
- ['timestamp', ISO8601 date] - When the weight was measured
Examples
json { "kind": 1351, "content": "70", "tags": [ ["unit", "kg"], ["t", "health"], ["t", "weight"] ] }json { "kind": 1351, "content": "154", "tags": [ ["unit", "lb"], ["t", "health"], ["t", "weight"], ["converted_value", "69.85", "kg"] ] }NIP-101h.2: Height
Status: Draft
Description
This NIP defines the format for storing and sharing height data on Nostr.
Event Kind: 1352
Content
The content field can use two formats: - For metric height: A string containing the numeric height value in centimeters (cm) - For imperial height: A JSON string with feet and inches properties
Required Tags
['t', 'health']- Categorization tag['t', 'height']- Specific metric tag['unit', 'cm' or 'imperial']- Unit of measurement
Optional Tags
['converted_value', value, 'cm']- Provides height in centimeters for interoperability when imperial is used['timestamp', ISO8601-date]- When the height was measured
Examples
```jsx // Example 1: Metric height Apply to App.jsx
// Example 2: Imperial height with conversion Apply to App.jsx ```
Implementation Notes
- Centimeters (cm) is the canonical unit for height interoperability
- When using imperial units, a conversion to centimeters SHOULD be provided
- Height values SHOULD be positive integers
- For maximum compatibility, clients SHOULD support both formats
NIP-101h.3: Age
Status: Draft
Description
This NIP defines the format for storing and sharing age data on Nostr.
Event Kind: 1353
Content
The content field MUST contain the numeric age value as a string.
Required Tags
['unit', 'years']- Unit of measurement['t', 'health']- Categorization tag['t', 'age']- Specific metric tag
Optional Tags
['timestamp', ISO8601-date]- When the age was recorded['dob', ISO8601-date]- Date of birth (if the user chooses to share it)
Examples
```jsx // Example 1: Basic age Apply to App.jsx
// Example 2: Age with DOB Apply to App.jsx ```
Implementation Notes
- Age SHOULD be represented as a positive integer
- For privacy reasons, date of birth (dob) is optional
- Clients SHOULD consider updating age automatically if date of birth is known
- Age can be a sensitive metric and clients may want to consider encrypting this data
NIP-101h.4: Gender
Status: Draft
Description
This NIP defines the format for storing and sharing gender data on Nostr.
Event Kind: 1354
Content
The content field contains a string representing the user's gender.
Required Tags
['t', 'health']- Categorization tag['t', 'gender']- Specific metric tag
Optional Tags
['timestamp', ISO8601-date]- When the gender was recorded['preferred_pronouns', string]- User's preferred pronouns
Common Values
While any string value is permitted, the following common values are recommended for interoperability: - male - female - non-binary - other - prefer-not-to-say
Examples
```jsx // Example 1: Basic gender Apply to App.jsx
// Example 2: Gender with pronouns Apply to App.jsx ```
Implementation Notes
- Clients SHOULD allow free-form input for gender
- For maximum compatibility, clients SHOULD support the common values
- Gender is a sensitive personal attribute and clients SHOULD consider appropriate privacy controls
- Applications focusing on health metrics should be respectful of gender diversity
NIP-101h.5: Fitness Level
Status: Draft
Description
This NIP defines the format for storing and sharing fitness level data on Nostr.
Event Kind: 1355
Content
The content field contains a string representing the user's fitness level.
Required Tags
['t', 'health']- Categorization tag['t', 'fitness']- Fitness category tag['t', 'level']- Specific metric tag
Optional Tags
['timestamp', ISO8601-date]- When the fitness level was recorded['activity', activity-type]- Specific activity the fitness level relates to['metrics', JSON-string]- Quantifiable fitness metrics used to determine level
Common Values
While any string value is permitted, the following common values are recommended for interoperability: - beginner - intermediate - advanced - elite - professional
Examples
```jsx // Example 1: Basic fitness level Apply to App.jsx
// Example 2: Activity-specific fitness level with metrics Apply to App.jsx ```
Implementation Notes
- Fitness level is subjective and may vary by activity
- The activity tag can be used to specify fitness level for different activities
- The metrics tag can provide objective measurements to support the fitness level
- Clients can extend this format to include activity-specific fitness assessments
- For general fitness apps, the simple beginner/intermediate/advanced scale is recommended
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ 99e7936f:d5d2197c
2025-05-16 13:09:05
@ 99e7936f:d5d2197c
2025-05-16 13:09:05Baustelle HERZ
Können wir nicht einfach glücklich sein? Nein.
Eine traumatisierte Gesellschaft kann nicht EINFACH glücklich sein, weil die Herzen verletzt sind.
„Ja, aber es gibt doch auch noch andere Probleme als Trauma“, kritisieren einige.
„Ich habe schließlich eine Familie und einen anstrengenden Job“, erklären andere.
„Für mich ist das eine abstrakte Diskussion, ein Luxusproblem“, geben manche zu bedenken.
„Eigentlich möchte ich mich mit dem Thema gar nicht beschäftigen“, sagen wenige, denken aber viele.
„Ich beschäftige mich lieber mit positiven Dingen“, ist die diplomatische Variante der Vermeidung dieses Themas.
Niemand redet gerne über Trauma, bis es an die eigene Tür klopft. Und dann ist guter Rat teuer. Dann würde man gerne reden, aber die anderen wollen immer noch nicht.
Niemand redet gerne über Trauma.
„Was heißt denn Anklopfen?“ Mit Anklopfen meine ich die Situationen, die jeder kennt. Gemeint sind ganz normale Lebenskrisen, die es mehrmals in jedem Leben gibt.
„Ist denn eine Lebenskrise gleichzusetzten mit einem Trauma?“ Nein, aber durch eine starke Lebenskrise kann ein altes Trauma wieder hochgespült werden, und das fühlt sich dann original so an, wie das Trauma, das man z.B. als Kind oder später im Leben erlebt hat.
Und das passiert in einer traumatisierten Gesellschaft ständig, nur nennen die Leute es nicht so. Niemand sagt: „Er oder sie hat ein aktiviertes Trauma.“
Hierzu habe ich eine Anekdote. Vor ein paar Monaten zog in das Nachbarhaus bei mir auf der Straße ein junger Mann ein. Das Haus war frisch renoviert worden. Es zogen zeitgleich mehrere junge Leute jeweils in eine Wohnung dieses Hauses ein. Die Stimmung im Haus war gut, weil alles neu und geschmackvoll gestaltet worden war und die Mieter gut zusammen passten. Dann merkten die Mieter und Nachbarn, dass es einem jungen Mann nicht gut ging. Er saß den ganzen Tag in der Wohnung, konnte sich zu nichts aufraffen. Er schaffte es nicht, sich Lebensmittel einzukaufen. Ein Freund kam regelmäßig vorbei und brachte ihm Essen. Eine ältere Nachbarin fragte nach einigen Monaten diesen Freund, was dem jungen Mann denn fehle, ob er eine Krankheit habe oder was denn los sei. Der Freund lachte und sagte nur einen Satz: „Er stirbt.“
Die Nachbarin erzählte mir das und schaute mich fragend an. Ich übersetzte ihr den Satz und meinte: „Er hat vermutlich Liebeskummer.“ Aber was ich wirklich dachte, war, dass er ein aktiviertes Trauma hatte, nur sagte ich das nicht zur Nachbarin. Nach mittlerweile zwei Jahren kommt der Freund immer noch regelmäßig und bringt dem jungen Mann Essen. Er kauft für ihn ein und kümmert sich um ihn.
Manche Menschen leiden sehr lange unter Verlusten, Zurückweisungen, Niederlagen, Verletzungen. Andere kommen nie auf die nächste Stufe, obwohl sie sich unaufhörlich anstrengen. Wieder andere haben alles und sind dennoch unzufrieden und in permanenter Angriffshaltung. All diese Phänomene dauern oft lange, manchmal sogar ein Leben lang. Meines Erachtens sind das aktivierte Traumen bzw. Traumen, die gut verschlossen dennoch im Unterbewusstsein gegen die eigene Person arbeiten.
Trauma hat viele Gesichter.
Es kommt bei den unmöglichsten Gelegenheiten zum Vorschein. Und oft erkennen wir es nicht als das, was es ist. Wir suchen den Grund im Außen, den es ja meist auch gibt. Nur ist der Grund nicht der Grund, sondern nur der Auslöser.
Auch ich bin einmal „gestorben“. Dieser Zustand dauerte über drei Jahre an. Deshalb klingelte es bei mir auch sofort im Ohr als die Nachbarin sagte, der Freund habe gesagt: „Er stirbt.“
Sprache ist wunderbar.
Wer beides schon mal erlebt hat, eine normale Trennung und eine schwere Trennung, einen normalen Arbeitsplatzwechsel oder einen dramatischen Jobverlust, ein geplatztes Geschäft oder einen geplatzten Lebenstraum, das Ende einer Freundschaft oder eine Kränkung, über die man noch nach 35 Jahren so berichtet, als ob es gestern gewesen wäre, der kennt den Unterschied in der Intensität der Gefühle. Manche Menschen erzählen immer wieder eine Geschichte, obwohl man sie schon kennt und auch sein Mitgefühl dazu ausgedrückt hat. Manche Menschen reden gar nicht mehr über eine bestimmte Sache, bis einem irgendwann von Dritten gesagt wird, dass man ihn oder sie besser nicht auf das Thema XYZ ansprechen sollte.
All das sind aktivierte Traumen, die noch weh tun, noch nicht verarbeitet sind. Es sind Dinge, die jedem von uns passieren können. Jeder erlebt im Leben partnerschaftliche Trennungen, geplatzte Geschäfte und Kränkungen am laufenden Meter, aber es „trifft“ einen nicht immer gleich. Und es trifft nicht nur die Sensiblen, sondern es trifft jeden, wenn der Punkt, an dem es trifft, wund ist. Der wunde Punkt macht jeden sensibel. Auch robuste Naturen haben einen wunden Punkt. Und wenn der getroffen wird, dann werden auch die härtesten Menschen butterweich. In einer traumatisierten Gesellschaft wird jeder so oft „getroffen“, wie es braucht, bis er sich dem Thema widmet. Wir alle haben diese frühen oder späten Traumen erlebt, die früher oder später erneut durch Krisen aktiviert werden. Und dann „sterben“ wir, zumindest gefühlt.
Denn Trauma ist immer existenziell.
Und aktiviertes Trauma ist bitte nicht zu verwechseln mit Depression. Es ist ein aktiviertes Trauma, das sich im Unterschied zur Depression sehr wach, lebendig und vor allem schmerzvoll anfühlt. Es fühlt sich an wie „damals“. Das versteht man, in der Situation steckend, komischerweise sofort, denn wir haben ein Schmerzgedächtnis. Wir können Düfte oder Musik ja auch sofort zuordnen, wenn sie uns an etwas erinnern. Mit Schmerz ist es ähnlich. Aber es fällt so schwer, darüber zu reden, weil es keiner versteht und weil es dafür meines Erachtens in unserer Sprache keine Worte gibt. Man versteht das erst, wenn man es selbst erlebt hat. Und dann reichen zwei Worte.
Die Baustelle HERZ versteht man erst, wenn man selbst ein aktiviertes Trauma erlebt, durchlebt hat, wenn man einmal „gestorben“ ist.
Heute kann ich an Äußerungen, die jemand macht, gut ablesen, ob jemand seine Baustelle HERZ bereits kennen gelernt hat oder nicht. Menschen, die das selbst noch nicht kennen gelernt haben, haben oft aufmunternde Sprüche wie „Das wird schon wieder. Jetzt lass den Kopf mal nicht hängen.“ Das hilft einem dann in etwa so, wie wenn man in einer Depression gesagt bekommt: „Nun lach doch mal.“ Man weiß dann sofort, welchen Erfahrungshintergrund das Gegenüber hat. Das ist keine Wertung, nur eine Feststellung. Unsere Kultur hat hier einfach wichtiges Wissen verloren. Ich persönlich weiß nicht, wie es ist, ein Kind auf die Welt zu bringen oder ein Kind zu verlieren. Ich weiß vieles nicht und habe vermutlich auch schon wenig hilfreiche Kommentare abgegeben, weil ich es nicht besser wusste. Aber ich weiß, wie sich ein aktiviertes Trauma anfühlt. Und das ist ein wertvolles Wissen, was ich gern teilen möchte. Man schaut mit diesem erfahrenen Wissen (kein Bücher-Wissen) viel differenzierter auf das Leid anderer Menschen. Es gibt so viele Sorten von Trauma und deswegen auch Sorten von aktiviertem Trauma. Manchmal denkt man sich nichts dabei und sagt etwas, und schon hat man beim anderen einen Punkt getroffen, der dadurch nun schmerzt. Wenn man Glück hat, dann dauert der Schmerz nur kurz an. Wenn man Pech hat, ist die Freundschaft zu Ende. Ich habe das selbst schon erlebt. Mal war ich es, die den Rückzug angetreten hat. Mal war es der andere. Hinter diesen Phänomenen steckt nichtverarbeitetes Trauma. Die Bildungslücke bezüglich Trauma in unserer Gesellschaft ist (gewollt) riesig.
Wir sind eine traumatisierte Gesellschaft, die nicht weiß, dass sie eine traumatisierte Gesellschaft ist.
Viele Menschen haben unverarbeitetes Trauma im Gepäck. Wir haben selbst nach Jahren der Therapie und Selbstreflektion immer noch unverarbeitete Anteile eines Traumas im Gepäck, das wir glaubten, bearbeitet zu haben. Mir ist das bewusst geworden, je besser ich mein eigenes Trauma kennen und lieben gelernt habe.
Eigentlich wollte ich heute kurz etwas über den gesunden Umgang mit Gefühlen schreiben. Beim Schreiben habe ich aber gemerkt, dass ich erstmal etwas über das Haus erzählen muss, bevor ich über die Gäste, die Gefühle, rede. Ich bin das Haus, das durch Verstand und Gefühle belebt wird. Und hinter dem Haus gibt es noch ein ganzes Universum, auf das ich heute nicht eingehen möchte.
Gefühle und Fühlen sind zentral wichtig, wenn man Trauma bearbeiten möchte.
Trauma wird solange aktiviert, bis es bearbeitet wurde.
In einer traumatisierten Gesellschaft wird 24/7 Trauma aktiviert. Und das ist gut so. Die Evolution schläft nicht. Die Evolution schenkt uns Schmerz, damit wir ihr Aufmerksamkeit schenken.
Das Leben liebt uns, und wiederkehrender Schmerz ist wie die Schlummerfunktion am Wecker, die möchte, dass wir aufwachen.
In unserer traumatisierten Gesellschaft klingelt momentan nicht nur der Wecker. Alles, was tönen kann, gibt Signal. Mir kommt es in dieser Zeit manchmal vor, wie wenn sich gleichzeitig , das Kinder-Sinfonieorchester mit sämtlichen Instrumenten einstimmt, jemand mit dem Handy telefoniert, das Fenster zur Hauptstraße offen steht, der Bus anfährt, der Auspuff röhrt, jemand hupt, das Martinshorn aufheult, die Drehorgel spielt, das Pausenzeichen in der Schule ertönt, es an der Tür klingelt und die Kirchenorgel aus allen Pfeifen flötet und brummt.
Aktiviertes Trauma macht ordentlich Krach individuell und erst recht gesellschaftlich gesehen. Und je lauter es ist, desto dringender möchte es bearbeitet werden.
Die Baustelle HERZ zu bearbeiten, lohnt sich. Und Fühlen bringt die Verwandlung.
-
 @ 8125b911:a8400883
2025-04-25 07:02:35
@ 8125b911:a8400883
2025-04-25 07:02:35In Nostr, all data is stored as events. Decentralization is achieved by storing events on multiple relays, with signatures proving the ownership of these events. However, if you truly want to own your events, you should run your own relay to store them. Otherwise, if the relays you use fail or intentionally delete your events, you'll lose them forever.
For most people, running a relay is complex and costly. To solve this issue, I developed nostr-relay-tray, a relay that can be easily run on a personal computer and accessed over the internet.
Project URL: https://github.com/CodyTseng/nostr-relay-tray
This article will guide you through using nostr-relay-tray to run your own relay.
Download
Download the installation package for your operating system from the GitHub Release Page.
| Operating System | File Format | | --------------------- | ---------------------------------- | | Windows |
nostr-relay-tray.Setup.x.x.x.exe| | macOS (Apple Silicon) |nostr-relay-tray-x.x.x-arm64.dmg| | macOS (Intel) |nostr-relay-tray-x.x.x.dmg| | Linux | You should know which one to use |Installation
Since this app isn’t signed, you may encounter some obstacles during installation. Once installed, an ostrich icon will appear in the status bar. Click on the ostrich icon, and you'll see a menu where you can click the "Dashboard" option to open the relay's control panel for further configuration.

macOS Users:
- On first launch, go to "System Preferences > Security & Privacy" and click "Open Anyway."
- If you encounter a "damaged" message, run the following command in the terminal to remove the restrictions:
bash sudo xattr -rd com.apple.quarantine /Applications/nostr-relay-tray.appWindows Users:
- On the security warning screen, click "More Info > Run Anyway."
Connecting
By default, nostr-relay-tray is only accessible locally through
ws://localhost:4869/, which makes it quite limited. Therefore, we need to expose it to the internet.In the control panel, click the "Proxy" tab and toggle the switch. You will then receive a "Public address" that you can use to access your relay from anywhere. It's that simple.
Next, add this address to your relay list and position it as high as possible in the list. Most clients prioritize connecting to relays that appear at the top of the list, and relays lower in the list are often ignored.

Restrictions
Next, we need to set up some restrictions to prevent the relay from storing events that are irrelevant to you and wasting storage space. nostr-relay-tray allows for flexible and fine-grained configuration of which events to accept, but some of this is more complex and will not be covered here. If you're interested, you can explore this further later.
For now, I'll introduce a simple and effective strategy: WoT (Web of Trust). You can enable this feature in the "WoT & PoW" tab. Before enabling, you'll need to input your pubkey.
There's another important parameter,
Depth, which represents the relationship depth between you and others. Someone you follow has a depth of 1, someone they follow has a depth of 2, and so on.- Setting this parameter to 0 means your relay will only accept your own events.
- Setting it to 1 means your relay will accept events from you and the people you follow.
- Setting it to 2 means your relay will accept events from you, the people you follow, and the people they follow.
Currently, the maximum value for this parameter is 2.

Conclusion
You've now successfully run your own relay and set a simple restriction to prevent it from storing irrelevant events.
If you encounter any issues during use, feel free to submit an issue on GitHub, and I'll respond as soon as possible.
Not your relay, not your events.
-
 @ e691f4df:1099ad65
2025-04-24 18:56:12
@ e691f4df:1099ad65
2025-04-24 18:56:12Viewing Bitcoin Through the Light of Awakening
Ankh & Ohm Capital’s Overview of the Psycho-Spiritual Nature of Bitcoin
Glossary:
I. Preface: The Logos of Our Logo
II. An Oracular Introduction
III. Alchemizing Greed
IV. Layers of Fractalized Thought
V. Permissionless Individuation
VI. Dispelling Paradox Through Resonance
VII. Ego Deflation
VIII. The Coin of Great Price
Preface: The Logos of Our Logo
Before we offer our lens on Bitcoin, it’s important to illuminate the meaning behind Ankh & Ohm’s name and symbol. These elements are not ornamental—they are foundational, expressing the cosmological principles that guide our work.
Our mission is to bridge the eternal with the practical. As a Bitcoin-focused family office and consulting firm, we understand capital not as an end, but as a tool—one that, when properly aligned, becomes a vehicle for divine order. We see Bitcoin not simply as a technological innovation but as an emanation of the Divine Logos—a harmonic expression of truth, transparency, and incorruptible structure. Both the beginning and the end, the Alpha and Omega.
The Ankh (☥), an ancient symbol of eternal life, is a key to the integration of opposites. It unites spirit and matter, force and form, continuity and change. It reminds us that capital, like Life, must not only be generative, but regenerative; sacred. Money must serve Life, not siphon from it.
The Ohm (Ω) holds a dual meaning. In physics, it denotes a unit of electrical resistance—the formative tension that gives energy coherence. In the Vedic tradition, Om (ॐ) is the primordial vibration—the sound from which all existence unfolds. Together, these symbols affirm a timeless truth: resistance and resonance are both sacred instruments of the Creator.
Ankh & Ohm, then, represents our striving for union, for harmony —between the flow of life and intentional structure, between incalculable abundance and measured restraint, between the lightbulb’s electrical impulse and its light-emitting filament. We stand at the threshold where intention becomes action, and where capital is not extracted, but cultivated in rhythm with the cosmos.
We exist to shepherd this transformation, as guides of this threshold —helping families, founders, and institutions align with a deeper order, where capital serves not as the prize, but as a pathway to collective Presence, Purpose, Peace and Prosperity.
An Oracular Introduction
Bitcoin is commonly understood as the first truly decentralized and secure form of digital money—a breakthrough in monetary sovereignty. But this view, while technically correct, is incomplete and spiritually shallow. Bitcoin is more than a tool for economic disruption. Bitcoin represents a mythic threshold: a symbol of the psycho-spiritual shift that many ancient traditions have long foretold.
For millennia, sages and seers have spoken of a coming Golden Age. In the Vedic Yuga cycles, in Plato’s Great Year, in the Eagle and Condor prophecies of the Americas—there exists a common thread: that humanity will emerge from darkness into a time of harmony, cooperation, and clarity. That the veil of illusion (maya, materiality) will thin, and reality will once again become transparent to the transcendent. In such an age, systems based on scarcity, deception, and centralization fall away. A new cosmology takes root—one grounded in balance, coherence, and sacred reciprocity.
But we must ask—how does such a shift happen? How do we cross from the age of scarcity, fear, and domination into one of coherence, abundance, and freedom?
One possible answer lies in the alchemy of incentive.
Bitcoin operates not just on the rules of computer science or Austrian economics, but on something far more old and subtle: the logic of transformation. It transmutes greed—a base instinct rooted in scarcity—into cooperation, transparency, and incorruptibility.
In this light, Bitcoin becomes more than code—it becomes a psychoactive protocol, one that rewires human behavior by aligning individual gain with collective integrity. It is not simply a new form of money. It is a new myth of value. A new operating system for human consciousness.
Bitcoin does not moralize. It harmonizes. It transforms the instinct for self-preservation into a pathway for planetary coherence.
Alchemizing Greed
At the heart of Bitcoin lies the ancient alchemical principle of transmutation: that which is base may be refined into gold.
Greed, long condemned as a vice, is not inherently evil. It is a distorted longing. A warped echo of the drive to preserve life. But in systems built on scarcity and deception, this longing calcifies into hoarding, corruption, and decay.
Bitcoin introduces a new game. A game with memory. A game that makes deception inefficient and truth profitable. It does not demand virtue—it encodes consequence. Its design does not suppress greed; it reprograms it.
In traditional models, game theory often illustrates the fragility of trust. The Prisoner’s Dilemma reveals how self-interest can sabotage collective well-being. But Bitcoin inverts this. It creates an environment where self-interest and integrity converge—where the most rational action is also the most truthful.
Its ledger, immutable and transparent, exposes manipulation for what it is: energetically wasteful and economically self-defeating. Dishonesty burns energy and yields nothing. The network punishes incoherence, not by decree, but by natural law.
This is the spiritual elegance of Bitcoin: it does not suppress greed—it transmutes it. It channels the drive for personal gain into the architecture of collective order. Miners compete not to dominate, but to validate. Nodes collaborate not through trust, but through mathematical proof.
This is not austerity. It is alchemy.
Greed, under Bitcoin, is refined. Tempered. Re-forged into a generative force—no longer parasitic, but harmonic.
Layers of Fractalized Thought Fragments
All living systems are layered. So is the cosmos. So is the human being. So is a musical scale.
At its foundation lies the timechain—the pulsing, incorruptible record of truth. Like the heart, it beats steadily. Every block, like a pulse, affirms its life through continuity. The difficulty adjustment—Bitcoin’s internal calibration—functions like heart rate variability, adapting to pressure while preserving coherence.
Above this base layer is the Lightning Network—a second layer facilitating rapid, efficient transactions. It is the nervous system: transmitting energy, reducing latency, enabling real-time interaction across a distributed whole.
Beyond that, emerging tools like Fedimint and Cashu function like the capillaries—bringing vitality to the extremities, to those underserved by legacy systems. They empower the unbanked, the overlooked, the forgotten. Privacy and dignity in the palms of those the old system refused to see.
And then there is NOSTR—the decentralized protocol for communication and creation. It is the throat chakra, the vocal cords of the “freedom-tech” body. It reclaims speech from the algorithmic overlords, making expression sovereign once more. It is also the reproductive system, as it enables the propagation of novel ideas and protocols in fertile, uncensorable soil.
Each layer plays its part. Not in hierarchy, but in harmony. In holarchy. Bitcoin and other open source protocols grow not through exogenous command, but through endogenous coherence. Like cells in an organism. Like a song.
Imagine the cell as a piece of glass from a shattered holographic plate —by which its perspectival, moving image can be restructured from the single shard. DNA isn’t only a logical script of base pairs, but an evolving progressive song. Its lyrics imbued with wise reflections on relationships. The nucleus sings, the cell responds—not by command, but by memory. Life is not imposed; it is expressed. A reflection of a hidden pattern.
Bitcoin chants this. Each node, a living cell, holds the full timechain—Truth distributed, incorruptible. Remove one, and the whole remains. This isn’t redundancy. It’s a revelation on the power of protection in Truth.
Consensus is communion. Verification becomes a sacred rite—Truth made audible through math.
Not just the signal; the song. A web of self-expression woven from Truth.
No center, yet every point alive with the whole. Like Indra’s Net, each reflects all. This is more than currency and information exchange. It is memory; a self-remembering Mind, unfolding through consensus and code. A Mind reflecting the Truth of reality at the speed of thought.
Heuristics are mental shortcuts—efficient, imperfect, alive. Like cells, they must adapt or decay. To become unbiased is to have self-balancing heuristics which carry feedback loops within them: they listen to the environment, mutate when needed, and survive by resonance with reality. Mutation is not error, but evolution. Its rules are simple, but their expression is dynamic.
What persists is not rigidity, but pattern.
To think clearly is not necessarily to be certain, but to dissolve doubt by listening, adjusting, and evolving thought itself.
To understand Bitcoin is simply to listen—patiently, clearly, as one would to a familiar rhythm returning.
Permissionless Individuation
Bitcoin is a path. One that no one can walk for you.
Said differently, it is not a passive act. It cannot be spoon-fed. Like a spiritual path, it demands initiation, effort, and the willingness to question inherited beliefs.
Because Bitcoin is permissionless, no one can be forced to adopt it. One must choose to engage it—compelled by need, interest, or intuition. Each person who embarks undergoes their own version of the hero’s journey.
Carl Jung called this process Individuation—the reconciliation of fragmented psychic elements into a coherent, mature Self. Bitcoin mirrors this: it invites individuals to confront the unconscious assumptions of the fiat paradigm, and to re-integrate their relationship to time, value, and agency.
In Western traditions—alchemy, Christianity, Kabbalah—the individual is sacred, and salvation is personal. In Eastern systems—Daoism, Buddhism, the Vedas—the self is ultimately dissolved into the cosmic whole. Bitcoin, in a paradoxical way, echoes both: it empowers the individual, while aligning them with a holistic, transcendent order.
To truly see Bitcoin is to allow something false to die. A belief. A habit. A self-concept.
In that death—a space opens for deeper connection with the Divine itSelf.
In that dissolution, something luminous is reborn.
After the passing, Truth becomes resurrected.
Dispelling Paradox Through Resonance
There is a subtle paradox encoded into the hero’s journey: each starts in solidarity, yet the awakening affects the collective.
No one can be forced into understanding Bitcoin. Like a spiritual truth, it must be seen. And yet, once seen, it becomes nearly impossible to unsee—and easier for others to glimpse. The pattern catches.
This phenomenon mirrors the concept of morphic resonance, as proposed and empirically tested by biologist Rupert Sheldrake. Once a critical mass of individuals begins to embody a new behavior or awareness, it becomes easier—instinctive—for others to follow suit. Like the proverbial hundredth monkey who begins to wash the fruit in the sea water, and suddenly, monkeys across islands begin doing the same—without ever meeting.
When enough individuals embody a pattern, it ripples outward. Not through propaganda, but through field effect and wave propagation. It becomes accessible, instinctive, familiar—even across great distance.
Bitcoin spreads in this way. Not through centralized broadcast, but through subtle resonance. Each new node, each individual who integrates the protocol into their life, strengthens the signal for others. The protocol doesn’t shout; it hums, oscillates and vibrates——persistently, coherently, patiently.
One awakens. Another follows. The current builds. What was fringe becomes familiar. What was radical becomes obvious.
This is the sacred geometry of spiritual awakening. One awakens, another follows, and soon the fluidic current is strong enough to carry the rest. One becomes two, two become many, and eventually the many become One again. This tessellation reverberates through the human aura, not as ideology, but as perceivable pattern recognition.
Bitcoin’s most powerful marketing tool is truth. Its most compelling evangelist is reality. Its most unstoppable force is resonance.
Therefore, Bitcoin is not just financial infrastructure—it is psychic scaffolding. It is part of the subtle architecture through which new patterns of coherence ripple across the collective field.
The training wheels from which humanity learns to embody Peace and Prosperity.
Ego Deflation
The process of awakening is not linear, and its beginning is rarely gentle—it usually begins with disruption, with ego inflation and destruction.
To individuate is to shape a center; to recognize peripherals and create boundaries—to say, “I am.” But without integration, the ego tilts—collapsing into void or inflating into noise. Fiat reflects this pathology: scarcity hoarded, abundance simulated. Stagnation becomes disguised as safety, and inflation masquerades as growth.
In other words, to become whole, the ego must first rise—claiming agency, autonomy, and identity. However, when left unbalanced, it inflates, or implodes. It forgets its context. It begins to consume rather than connect. And so the process must reverse: what inflates must deflate.
In the fiat paradigm, this inflation is literal. More is printed, and ethos is diluted. Savings decay. Meaning erodes. Value is abstracted. The economy becomes bloated with inaudible noise. And like the psyche that refuses to confront its own shadow, it begins to collapse under the weight of its own illusions.
But under Bitcoin, time is honored. Value is preserved. Energy is not abstracted but grounded.
Bitcoin is inherently deflationary—in both economic and spiritual senses. With a fixed supply, it reveals what is truly scarce. Not money, not status—but the finite number of heartbeats we each carry.
To see Bitcoin is to feel that limit in one’s soul. To hold Bitcoin is to feel Time’s weight again. To sense the importance of Bitcoin is to feel the value of preserved, potential energy. It is to confront the reality that what matters cannot be printed, inflated, or faked. In this way, Bitcoin gently confronts the ego—not through punishment, but through clarity.
Deflation, rightly understood, is not collapse—it is refinement. It strips away illusion, bloat, and excess. It restores the clarity of essence.
Spiritually, this is liberation.
The Coin of Great Price
There is an ancient parable told by a wise man:
“The kingdom of heaven is like a merchant seeking fine pearls, who, upon finding one of great price, sold all he had and bought it.”
Bitcoin is such a pearl.
But the ledger is more than a chest full of treasure. It is a key to the heart of things.
It is not just software—it is sacrament.
A symbol of what cannot be corrupted. A mirror of divine order etched into code. A map back to the sacred center.
It reflects what endures. It encodes what cannot be falsified. It remembers what we forgot: that Truth, when aligned with form, becomes Light once again.
Its design is not arbitrary. It speaks the language of life itself—
The elliptic orbits of the planets mirrored in its cryptography,
The logarithmic spiral of the nautilus shell discloses its adoption rate,
The interconnectivity of mycelium in soil reflect the network of nodes in cyberspace,
A webbed breadth of neurons across synaptic space fires with each new confirmed transaction.
It is geometry in devotion. Stillness in motion.
It is the Logos clothed in protocol.
What this key unlocks is beyond external riches. It is the eternal gold within us.
Clarity. Sovereignty. The unshakeable knowing that what is real cannot be taken. That what is sacred was never for sale.
Bitcoin is not the destination.
It is the Path.
And we—when we are willing to see it—are the Temple it leads back to.
-
 @ 40b9c85f:5e61b451
2025-04-24 15:27:02
@ 40b9c85f:5e61b451
2025-04-24 15:27:02Introduction
Data Vending Machines (DVMs) have emerged as a crucial component of the Nostr ecosystem, offering specialized computational services to clients across the network. As defined in NIP-90, DVMs operate on an apparently simple principle: "data in, data out." They provide a marketplace for data processing where users request specific jobs (like text translation, content recommendation, or AI text generation)
While DVMs have gained significant traction, the current specification faces challenges that hinder widespread adoption and consistent implementation. This article explores some ideas on how we can apply the reflection pattern, a well established approach in RPC systems, to address these challenges and improve the DVM ecosystem's clarity, consistency, and usability.
The Current State of DVMs: Challenges and Limitations
The NIP-90 specification provides a broad framework for DVMs, but this flexibility has led to several issues:
1. Inconsistent Implementation
As noted by hzrd149 in "DVMs were a mistake" every DVM implementation tends to expect inputs in slightly different formats, even while ostensibly following the same specification. For example, a translation request DVM might expect an event ID in one particular format, while an LLM service could expect a "prompt" input that's not even specified in NIP-90.
2. Fragmented Specifications
The DVM specification reserves a range of event kinds (5000-6000), each meant for different types of computational jobs. While creating sub-specifications for each job type is being explored as a possible solution for clarity, in a decentralized and permissionless landscape like Nostr, relying solely on specification enforcement won't be effective for creating a healthy ecosystem. A more comprehensible approach is needed that works with, rather than against, the open nature of the protocol.
3. Ambiguous API Interfaces
There's no standardized way for clients to discover what parameters a specific DVM accepts, which are required versus optional, or what output format to expect. This creates uncertainty and forces developers to rely on documentation outside the protocol itself, if such documentation exists at all.
The Reflection Pattern: A Solution from RPC Systems
The reflection pattern in RPC systems offers a compelling solution to many of these challenges. At its core, reflection enables servers to provide metadata about their available services, methods, and data types at runtime, allowing clients to dynamically discover and interact with the server's API.
In established RPC frameworks like gRPC, reflection serves as a self-describing mechanism where services expose their interface definitions and requirements. In MCP reflection is used to expose the capabilities of the server, such as tools, resources, and prompts. Clients can learn about available capabilities without prior knowledge, and systems can adapt to changes without requiring rebuilds or redeployments. This standardized introspection creates a unified way to query service metadata, making tools like
grpcurlpossible without requiring precompiled stubs.How Reflection Could Transform the DVM Specification
By incorporating reflection principles into the DVM specification, we could create a more coherent and predictable ecosystem. DVMs already implement some sort of reflection through the use of 'nip90params', which allow clients to discover some parameters, constraints, and features of the DVMs, such as whether they accept encryption, nutzaps, etc. However, this approach could be expanded to provide more comprehensive self-description capabilities.
1. Defined Lifecycle Phases
Similar to the Model Context Protocol (MCP), DVMs could benefit from a clear lifecycle consisting of an initialization phase and an operation phase. During initialization, the client and DVM would negotiate capabilities and exchange metadata, with the DVM providing a JSON schema containing its input requirements. nip-89 (or other) announcements can be used to bootstrap the discovery and negotiation process by providing the input schema directly. Then, during the operation phase, the client would interact with the DVM according to the negotiated schema and parameters.
2. Schema-Based Interactions
Rather than relying on rigid specifications for each job type, DVMs could self-advertise their schemas. This would allow clients to understand which parameters are required versus optional, what type validation should occur for inputs, what output formats to expect, and what payment flows are supported. By internalizing the input schema of the DVMs they wish to consume, clients gain clarity on how to interact effectively.
3. Capability Negotiation
Capability negotiation would enable DVMs to advertise their supported features, such as encryption methods, payment options, or specialized functionalities. This would allow clients to adjust their interaction approach based on the specific capabilities of each DVM they encounter.
Implementation Approach
While building DVMCP, I realized that the RPC reflection pattern used there could be beneficial for constructing DVMs in general. Since DVMs already follow an RPC style for their operation, and reflection is a natural extension of this approach, it could significantly enhance and clarify the DVM specification.
A reflection enhanced DVM protocol could work as follows: 1. Discovery: Clients discover DVMs through existing NIP-89 application handlers, input schemas could also be advertised in nip-89 announcements, making the second step unnecessary. 2. Schema Request: Clients request the DVM's input schema for the specific job type they're interested in 3. Validation: Clients validate their request against the provided schema before submission 4. Operation: The job proceeds through the standard NIP-90 flow, but with clearer expectations on both sides
Parallels with Other Protocols
This approach has proven successful in other contexts. The Model Context Protocol (MCP) implements a similar lifecycle with capability negotiation during initialization, allowing any client to communicate with any server as long as they adhere to the base protocol. MCP and DVM protocols share fundamental similarities, both aim to expose and consume computational resources through a JSON-RPC-like interface, albeit with specific differences.
gRPC's reflection service similarly allows clients to discover service definitions at runtime, enabling generic tools to work with any gRPC service without prior knowledge. In the REST API world, OpenAPI/Swagger specifications document interfaces in a way that makes them discoverable and testable.
DVMs would benefit from adopting these patterns while maintaining the decentralized, permissionless nature of Nostr.
Conclusion
I am not attempting to rewrite the DVM specification; rather, explore some ideas that could help the ecosystem improve incrementally, reducing fragmentation and making the ecosystem more comprehensible. By allowing DVMs to self describe their interfaces, we could maintain the flexibility that makes Nostr powerful while providing the structure needed for interoperability.
For developers building DVM clients or libraries, this approach would simplify consumption by providing clear expectations about inputs and outputs. For DVM operators, it would establish a standard way to communicate their service's requirements without relying on external documentation.
I am currently developing DVMCP following these patterns. Of course, DVMs and MCP servers have different details; MCP includes capabilities such as tools, resources, and prompts on the server side, as well as 'roots' and 'sampling' on the client side, creating a bidirectional way to consume capabilities. In contrast, DVMs typically function similarly to MCP tools, where you call a DVM with an input and receive an output, with each job type representing a different categorization of the work performed.
Without further ado, I hope this article has provided some insight into the potential benefits of applying the reflection pattern to the DVM specification.
-
 @ 87fedb9f:0da83419
2025-05-16 12:45:01
@ 87fedb9f:0da83419
2025-05-16 12:45:01Push it! Push it! Push it!
That chant still echoes in my bones, not just from the gym, but from the inside out. I remember watching a bodybuilder once — the weight trembling above him, his muscles bulging and giving out, the spotters swooping in to catch the bar just in time. “Train to failure,” they said. “That’s how you grow.”
And it makes sense, doesn’t it? If you’re being chased by a wild beast, you run until your body gives out. That’s how we’re wired — to survive first and foremost, not necessarily to thrive.
But what if the house we’re building isn’t under threat from wolves? What if we’ve got stone-moving machines and time to breathe? What if we’re not being chased anymore… but we still act like we are?
See, survival patterns are sneaky. They wear masks. They show up in workouts and work days. They dress up in ambition, caffeine, and “just one more thing before I stop.”
I’ve never been a bodybuilder — my brother was — but I’ve tried that route in my own work life. Lift to failure. Push it. Every other day, I’d be nursing another injury to body and mind.
I wasn’t getting stronger. I was just breaking myself in cycles. Push, break, recover, repeat.
I see the same thing with brains. Push it. Adderall. More coffee. Keep going. Hit the wall. And then—collapse.
That’s not strengthening. That’s surviving pretending to be “powerful.”
What happens to the rest of your system when your brain is sucking up all the energy just to stay on task? You stop digesting. You stop feeling the sun on your skin. You stop enjoying your kids’ laughter. Everything feels like something to push through.
That isn’t thriving.
Thriving feels different. It’s alive, yes — there’s activation. But it’s not strained. When we’re in thriving mode, we’re with our energy, not yanking it out by the roots and forcing it to regrow. The muscles — or the mind — are engaged, fluid, expressive. Alive.
It’s a fine line. You can take the same exact action and fill it with stress.
I’ve done it. I’ve turned a perfectly normal task into a survival sprint. It feels ridiculous in hindsight — like, why did I make this email reply into a mountain climb?
Because my primitive brain still whispers, “If you don’t do this perfectly and fast, you’ll die.” Not literally. But the threat feels real. The imagined judgment, the self-criticism, the fear of not being enough — they’re imaginary lions in the tall grass of modern life.
I’ve used this system on myself. I’ve strained my nervous system like fingernails scraping rock to avoid a fall that was never coming.
That’s what we’re supposed to do, right? We bring survival force into every aspect. Into parenting. Into projects. Into relationships.
And we wonder why we’re tired all the time. Not sleepy tired — soul tired. That kind of tired that feels like you ran for your life… but all you did was sit at your desk.
Here’s what I know now: if you’re not actually in danger, you can stop living like you are.
You don’t have to push everything to the edge. You don’t have to prove your strength through strain. Strength can be alive in you — not torn, not depleted, but awake and sustaining.
And when we live from there, the recovery feels different, too. We’re not collapsing. We’re restoring.
We’re not dropping all the pieces and then forcing ourselves to pick them up… again! Instead, we’re crafting a thriving life from the pieces we find, fashion, and consciously put in place.
There’s a wisdom to building your foundation around thriving — not just surviving. And thriving starts with recognizing: it’s not life or death to get through your inbox. Your self-worth isn’t measured by how busy and depleted you are.
Look around. Are you stacking more and more iron to prove something? Or are you listening to the quiet whisper that says, “Yes, move… but don’t hurt yourself doing it.”
And in a life that tells you to push until you fail, choosing to rest and relish — choosing to feel alive rather than just alive-enough — might just be the truest strength there is.
Useful Concepts for Thriving in This Story
-
Primitive Brain\ The primitive brain keeps us on high alert even when we’re safe — it’s time to question whether the lion is real.
-
Unrushed\ Being unrushed is a radical shift from survival tempo to the rhythm of true aliveness.
-
Savvy\ Savvy invites us to work with our energy wisely, not destructively — to choose thriving over proving.
-
Vitality\ Vitality flows when we stop draining ourselves for performance and start living from inner strength.
-
Inspired Action\ Inspired action arises from presence and aliveness, not adrenaline and depletion.
-
-
 @ 6e64b83c:94102ee8
2025-04-23 20:23:34
@ 6e64b83c:94102ee8
2025-04-23 20:23:34How to Run Your Own Nostr Relay on Android with Cloudflare Domain
Prerequisites
- Install Citrine on your Android device:
- Visit https://github.com/greenart7c3/Citrine/releases
- Download the latest release using:
- zap.store
- Obtainium
- F-Droid
- Or download the APK directly
-
Note: You may need to enable "Install from Unknown Sources" in your Android settings
-
Domain Requirements:
- Purchase a domain if you don't have one
-
Transfer your domain to Cloudflare if it's not already there (for free SSL certificates and cloudflared support)
-
Tools to use:
- nak (the nostr army knife):
- Download from https://github.com/fiatjaf/nak/releases
- Installation steps:
-
For Linux/macOS: ```bash # Download the appropriate version for your system wget https://github.com/fiatjaf/nak/releases/latest/download/nak-linux-amd64 # for Linux # or wget https://github.com/fiatjaf/nak/releases/latest/download/nak-darwin-amd64 # for macOS
# Make it executable chmod +x nak-*
# Move to a directory in your PATH sudo mv nak-* /usr/local/bin/nak
- For Windows:batch # Download the Windows version curl -L -o nak.exe https://github.com/fiatjaf/nak/releases/latest/download/nak-windows-amd64.exe# Move to a directory in your PATH (e.g., C:\Windows) move nak.exe C:\Windows\nak.exe
- Verify installation:bash nak --version ```
Setting Up Citrine
- Open the Citrine app
- Start the server
- You'll see it running on
ws://127.0.0.1:4869(local network only) - Go to settings and paste your npub into "Accept events signed by" inbox and press the + button. This prevents others from publishing events to your personal relay.
Installing Required Tools
- Install Termux from Google Play Store
- Open Termux and run:
bash pkg update && pkg install wget wget https://github.com/cloudflare/cloudflared/releases/latest/download/cloudflared-linux-arm64.deb dpkg -i cloudflared-linux-arm64.debCloudflare Authentication
- Run the authentication command:
bash cloudflared tunnel login - Follow the instructions:
- Copy the provided URL to your browser
- Log in to your Cloudflare account
- If the URL expires, copy it again after logging in
Creating the Tunnel
- Create a new tunnel:
bash cloudflared tunnel create <TUNNEL_NAME> - Choose any name you prefer for your tunnel
-
Copy the tunnel ID after creating the tunnel
-
Create and configure the tunnel config:
bash touch ~/.cloudflared/config.yml nano ~/.cloudflared/config.yml -
Add this configuration (replace the placeholders with your values): ```yaml tunnel:
credentials-file: /data/data/com.termux/files/home/.cloudflared/ .json ingress: - hostname: nostr.yourdomain.com service: ws://localhost:4869
- service: http_status:404 ```
- Note: In nano editor:
CTRL+Oand Enter to saveCTRL+Xto exit
-
Note: Check the credentials file path in the logs
-
Validate your configuration:
bash cloudflared tunnel validate -
Start the tunnel:
bash cloudflared tunnel run my-relay
Preventing Android from Killing the Tunnel
Run these commands to maintain tunnel stability:
bash date && apt install termux-tools && termux-setup-storage && termux-wake-lock echo "nameserver 1.1.1.1" > $PREFIX/etc/resolv.confTip: You can open multiple Termux sessions by swiping from the left edge of the screen while keeping your tunnel process running.
Updating Your Outbox Model Relays
Once your relay is running and accessible via your domain, you'll want to update your relay list in the Nostr network. This ensures other clients know about your relay and can connect to it.
Decoding npub (Public Key)
Private keys (nsec) and public keys (npub) are encoded in bech32 format, which includes: - A prefix (like nsec1, npub1 etc.) - The encoded data - A checksum
This format makes keys: - Easy to distinguish - Hard to copy incorrectly
However, most tools require these keys in hexadecimal (hex) format.
To decode an npub string to its hex format:
bash nak decode nostr:npub1dejts0qlva8mqzjlrxqkc2tmvs2t7elszky5upxaf3jha9qs9m5q605uc4Change it with your own npub.
bash { "pubkey": "6e64b83c1f674fb00a5f19816c297b6414bf67f015894e04dd4c657e94102ee8" }Copy the pubkey value in quotes.
Create a kind 10002 event with your relay list:
- Include your new relay with write permissions
- Include other relays you want to read from and write to, omit 3rd parameter to make it both read and write
Example format:
json { "kind": 10002, "tags": [ ["r", "wss://your-relay-domain.com", "write"], ["r", "wss://eden.nostr.land/"], ["r", "wss://nos.lol/"], ["r", "wss://nostr.bitcoiner.social/"], ["r", "wss://nostr.mom/"], ["r", "wss://relay.primal.net/"], ["r", "wss://nostr.wine/", "read"], ["r", "wss://relay.damus.io/"], ["r", "wss://relay.nostr.band/"], ["r", "wss://relay.snort.social/"] ], "content": "" }Save it to a file called
event.jsonNote: Add or remove any relays you want. To check your existing 10002 relays: - Visit https://nostr.band/?q=by%3Anpub1dejts0qlva8mqzjlrxqkc2tmvs2t7elszky5upxaf3jha9qs9m5q605uc4+++kind%3A10002 - nostr.band is an indexing service, it probably has your relay list. - Replace
npub1xxxin the URL with your own npub - Click "VIEW JSON" from the menu to see the raw event - Or use thenaktool if you know the relaysbash nak req -k 10002 -a <your-pubkey> wss://relay1.com wss://relay2.comReplace `<your-pubkey>` with your public key in hex format (you can get it using `nak decode <your-npub>`)- Sign and publish the event:
- Use a Nostr client that supports kind 10002 events
- Or use the
nakcommand-line tool:bash nak event --sec ncryptsec1... wss://relay1.com wss://relay2.com $(cat event.json)
Important Security Notes: 1. Never share your nsec (private key) with anyone 2. Consider using NIP-49 encrypted keys for better security 3. Never paste your nsec or private key into the terminal. The command will be saved in your shell history, exposing your private key. To clear the command history: - For bash: use
history -c- For zsh: usefc -Wto write history to file, thenfc -pto read it back - Or manually edit your shell history file (e.g.,~/.zsh_historyor~/.bash_history) 4. if you're usingzsh, usefc -pto prevent the next command from being saved to history 5. Or temporarily disable history before running sensitive commands:bash unset HISTFILE nak key encrypt ... set HISTFILEHow to securely create NIP-49 encypted private key
```bash
Read your private key (input will be hidden)
read -s SECRET
Read your password (input will be hidden)
read -s PASSWORD
encrypt command
echo "$SECRET" | nak key encrypt "$PASSWORD"
copy and paste the ncryptsec1 text from the output
read -s ENCRYPTED nak key decrypt "$ENCRYPTED"
clear variables from memory
unset SECRET PASSWORD ENCRYPTED ```
On a Windows command line, to read from stdin and use the variables in
nakcommands, you can use a combination ofset /pto read input and then use those variables in your command. Here's an example:```bash @echo off set /p "SECRET=Enter your secret key: " set /p "PASSWORD=Enter your password: "
echo %SECRET%| nak key encrypt %PASSWORD%
:: Clear the sensitive variables set "SECRET=" set "PASSWORD=" ```
If your key starts with
ncryptsec1, thenaktool will securely prompt you for a password when using the--secparameter, unless the command is used with a pipe< >or|.bash nak event --sec ncryptsec1... wss://relay1.com wss://relay2.com $(cat event.json)- Verify the event was published:
- Check if your relay list is visible on other relays
-
Use the
naktool to fetch your kind 10002 events:bash nak req -k 10002 -a <your-pubkey> wss://relay1.com wss://relay2.com -
Testing your relay:
- Try connecting to your relay using different Nostr clients
- Verify you can both read from and write to your relay
- Check if events are being properly stored and retrieved
- Tip: Use multiple Nostr clients to test different aspects of your relay
Note: If anyone in the community has a more efficient method of doing things like updating outbox relays, please share your insights in the comments. Your expertise would be greatly appreciated!
-
 @ 8f69ac99:4f92f5fd
2025-05-16 11:40:35
@ 8f69ac99:4f92f5fd
2025-05-16 11:40:35Há algo quase reconfortante na previsibilidade com que certos colunistas abordam Bitcoin: a cada oportunidade, repetem os mesmos chavões, reciclados com indignação moralista e embrulhados numa embalagem de falsa autoridade. O artigo publicado na Visão, com o título dramático "De criança prodígio a adolescente problemático", encaixa-se perfeitamente nesse molde.
Trata-se de uma peça de opinião que mistura factos irrelevantes com interpretações enviesadas, estatísticas sem contexto e um medo mal disfarçado de perder o monopólio da narrativa económica. A autora, Sofia Santos Machado, opta por colar em Bitcoin os desastres do chamado “mundo cripto” como se fossem parte do mesmo fenómeno — ignorando, por conveniência ou ignorância, que Bitcoin não é altcoins, não é NFTs, não é esquemas de yield exótico, e não é fintech vestida de blockchain.
Esta resposta centra-se exclusivamente em Bitcoin — um protocolo monetário aberto, incorruptível e resistente à censura, que já está a servir como salvaguarda de valor em regiões onde o sistema financeiro convencional falhou. Não me interessa defender pirâmides, tokens inflacionários ou aventuras bancárias mal calculadas.
Criticar Bitcoin é legítimo — mas fazê-lo sem saber do que se fala é apenas desinformação.
A Histeria da Água — Falar Sem Saber
O artigo abre com uma pérola alarmista sobre o consumo de água:
“Uma única transacção de bitcoin consome seis milhões de vezes mais água do que um pagamento com cartão.”
Seis. Milhões. De vezes. Resta saber se a autora escreveu isto com cara séria ou a rir-se enquanto bebia água engarrafada dos Alpes Suíços.
Fontes? Metodologia? Contexto? Estou a brincar — isto é a Visão, onde os números são decoração e os factos opcionais.
Claro que comparar transacções na camada base de Bitcoin com pagamentos "instantâneos" da rede Visa é tão rigoroso como comparar um Boeing 747 com um avião de papel porque um voa mais longe. Um artigo sério teria falado em batching, na Lightning Network, ou no facto de que Bitcoin nem sequer compete com a Visa nesse nível, nem em nenhum. Mas isso exigiria, imagine-se, investigação.
Pior ainda, não há qualquer menção ao consumo de água na extracção de ouro, nos data centers bancários, ou no treino de modelos de inteligência artificial. Pelos vistos, só Bitcoin tem de obedecer aos mandamentos ecológicos da Visão. O resto? Santa ignorância selectiva.
Criminosos e o Fantasma do Satoshi
Eis o clássico: “Bitcoin é usado por criminosos”. Um cliché bafiento tirado do baú de 2013, agora reapresentado como se fosse escândalo fresco.
Na realidade, Bitcoin é pseudónimo, não anónimo. Todas as transacções ficam gravadas num livro público — não é propriamente o esconderijo ideal para lavar dinheiro, a menos que sejas fã de disfarces em néon.
E os dados? Claríssimos. Segundo a Chainalysis e a Europol, a actividade ilícita com Bitcoin tem vindo a diminuir. Enquanto isso, os bancos — esses bastiões de confiança — continuam a ser apanhados a lavar biliões para cartéis e cleptocratas. Mas disso a Visão não fala. Devia estragar a narrativa.
O verdadeiro crime aqui é a preguiça intelectual tão profunda que quase merece uma moldura. A Visão tem um editor?
O Espantalho Energético
Como uma criança que acabou de aprender uma palavra nova, a Visão repete “consumo energético” como se fosse um pecado original. Bitcoin usa electricidade — escândalo!
Mas vejamos: o Proof-of-Work não é um defeito. É a razão pela qual Bitcoin é seguro. Não há “desperdício” — há uso, e muitas vezes com energia excedente, renovável, ou que de outro modo seria desperdiçada. É por isso que os mineiros se instalam junto a barragens remotas, queima de gás (flaring), ou parques eólicos no meio do nada — não porque odeiam o planeta, mas porque os incentivos económicos funcionam. Escrevi sobre isso aqui.
O que a Visão convenientemente ignora é que Bitcoin está a ajudar a integrar mais energia renovável nas redes, funcionando como carga flexível. Mas nuance? Trabalho de casa? Esquece lá isso.
Para uma explicação mais séria, podiam ter ouvido o podcast A Seita Bitcoin com o Daniel Batten. Mas para quê investigar?
Cripto = Bitcoin = Fraude?
Aqui chegamos ao buraco negro intelectual: enfiar tudo no mesmo saco. FTX colapsou? Culpa de Bitcoin. Um banqueiro jogou com altcoins? Culpa de Bitcoin. Scam de NFT? Deve ter sido o Satoshi.
Vamos esclarecer: Bitcoin não é “cripto”. Bitcoin é descentralizado, sem líderes, transparente. Não teve pré-mineração, não tem CEO, não promete lucros. O que o rodeia? Tokens centralizados, esquemas Ponzi, pirâmides e vaporware — precisamente o oposto do que Bitcoin representa.
Se um executivo bancário perde o dinheiro dos clientes em Dogecoins, isso é um problema dele. Bitcoin não lhe prometeu nada. Foi a ganância.
E convenhamos: os bancos tradicionais também colapsam. E não precisam de satoshis para isso. Bastam dívidas mal geridas, contabilidade criativa e uma fé cega no sistema.
Culpar Bitcoin por falcatruas “cripto” é como culpar o TCP/IP ou SMTP por emails de phishing. É preguiçoso, desonesto e diz-nos mais sobre a autora do que sobre a tecnologia.
Promessas Por Cumprir? Só Se Não Estiveres a Ver
A "jornalista" da Visão lamenta que “após 15 anos, os riscos são reais mas as promessas por cumprir”. Que promessas? Dinheiro grátis? Cafés pagos com QR codes mágicos?
Bitcoin nunca prometeu fazer cappuccinos mais rápidos. Prometeu soberania monetária, resistência à censura e um sistema previsível. E tem cumprido — diariamente, para milhões. E para o cappuccino, há sempre a Lightning Network.
Pergunta aos venezuelanos, nigerianos, peruanos ou argentinos se Bitcoin falhou. Para muitos, é a única forma de escapar à hiperinflação, ao confisco estatal e à decadência financeira.
Bitcoin não é uma app. É infra-estrutura. É uma nova camada base para o dinheiro global. Não se vê — mas protege, impõe regras e não obedece a caprichos de banqueiros centrais.
E isso assusta. Especialmente quem nunca viveu fora da bolha do euro.
Conclusão: A Visão a Gritar Contra o Progresso
No fim, o artigo da Visão é um festival de clichés, dados errados e ressentimento. Não é só enganador. É desonesto. Culpa a tecnologia pelos erros dos homens. Rejeita o futuro em nome do conforto passado.
Bitcoin não é uma varinha mágica. Mas é a fundação de uma nova liberdade financeira. Uma ferramenta para proteger valor, resistir a abusos e escapar ao controlo constante de quem acha que sabe o que é melhor para ti.
Portanto, fica aqui o desafio, Sofia: se queres criticar Bitcoin, primeiro percebe o que é. Lê o white paper. Estuda. Faz perguntas difíceis.
Caso contrário, és só mais um cão a ladrar para a trovoada — muito barulho, zero impacto.
-
 @ f32184ee:6d1c17bf
2025-04-23 13:21:52
@ f32184ee:6d1c17bf
2025-04-23 13:21:52Ads Fueling Freedom
Ross Ulbricht’s "Decentralize Social Media" painted a picture of a user-centric, decentralized future that transcended the limitations of platforms like the tech giants of today. Though focused on social media, his concept provided a blueprint for decentralized content systems writ large. The PROMO Protocol, designed by NextBlock while participating in Sovereign Engineering, embodies this blueprint in the realm of advertising, leveraging Nostr and Bitcoin’s Lightning Network to give individuals control, foster a multi-provider ecosystem, and ensure secure value exchange. In this way, Ulbricht’s 2021 vision can be seen as a prescient prediction of the PROMO Protocol’s structure. This is a testament to the enduring power of his ideas, now finding form in NextBlock’s innovative approach.
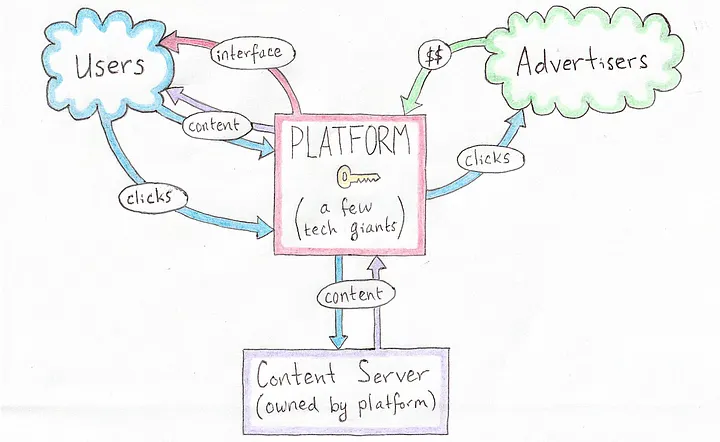 [Current Platform-Centric Paradigm, source: Ross Ulbricht's Decentralize Social Media]
[Current Platform-Centric Paradigm, source: Ross Ulbricht's Decentralize Social Media]Ulbricht’s Vision: A Decentralized Social Protocol
In his 2021 Medium article Ulbricht proposed a revolutionary vision for a decentralized social protocol (DSP) to address the inherent flaws of centralized social media platforms, such as privacy violations and inconsistent content moderation. Writing from prison, Ulbricht argued that decentralization could empower users by giving them control over their own content and the value they create, while replacing single, monolithic platforms with a competitive ecosystem of interface providers, content servers, and advertisers. Though his focus was on social media, Ulbricht’s ideas laid a conceptual foundation that strikingly predicts the structure of NextBlock’s PROMO Protocol, a decentralized advertising system built on the Nostr protocol.
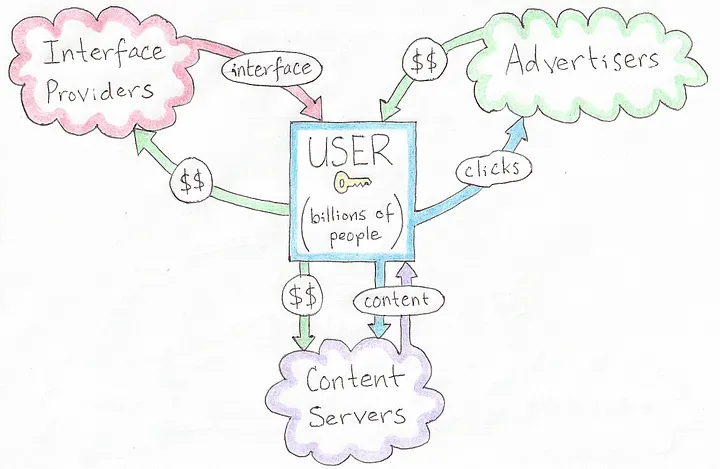 [A Decentralized Social Protocol (DSP), source: Ross Ulbricht's Decentralize Social Media]
[A Decentralized Social Protocol (DSP), source: Ross Ulbricht's Decentralize Social Media]Ulbricht’s Principles
Ulbricht’s article outlines several key principles for his DSP: * User Control: Users should own their content and dictate how their data and creations generate value, rather than being subject to the whims of centralized corporations. * Decentralized Infrastructure: Instead of a single platform, multiple interface providers, content hosts, and advertisers interoperate, fostering competition and resilience. * Privacy and Autonomy: Decentralized solutions for profile management, hosting, and interactions would protect user privacy and reduce reliance on unaccountable intermediaries. * Value Creation: Users, not platforms, should capture the economic benefits of their contributions, supported by decentralized mechanisms for transactions.
These ideas were forward-thinking in 2021, envisioning a shift away from the centralized giants dominating social media at the time. While Ulbricht didn’t specifically address advertising protocols, his framework for decentralization and user empowerment extends naturally to other domains, like NextBlock’s open-source offering: the PROMO Protocol.
NextBlock’s Implementation of PROMO Protocol
The PROMO Protocol powers NextBlock's Billboard app, a decentralized advertising protocol built on Nostr, a simple, open protocol for decentralized communication. The PROMO Protocol reimagines advertising by: * Empowering People: Individuals set their own ad prices (e.g., 500 sats/minute), giving them direct control over how their attention or space is monetized. * Marketplace Dynamics: Advertisers set budgets and maximum bids, competing within a decentralized system where a 20% service fee ensures operational sustainability. * Open-Source Flexibility: As an open-source protocol, it allows multiple developers to create interfaces or apps on top of it, avoiding the single-platform bottleneck Ulbricht critiqued. * Secure Payments: Using Strike Integration with Bitcoin Lightning Network, NextBlock enables bot-resistant and intermediary-free transactions, aligning value transfer with each person's control.
This structure decentralizes advertising in a way that mirrors Ulbricht’s broader vision for social systems, with aligned principles showing a specific use case: monetizing attention on Nostr.
Aligned Principles
Ulbricht’s 2021 article didn’t explicitly predict the PROMO Protocol, but its foundational concepts align remarkably well with NextBlock's implementation the protocol’s design: * Autonomy Over Value: Ulbricht argued that users should control their content and its economic benefits. In the PROMO Protocol, people dictate ad pricing, directly capturing the value of their participation. Whether it’s their time, influence, or digital space, rather than ceding it to a centralized ad network. * Ecosystem of Providers: Ulbricht envisioned multiple providers replacing a single platform. The PROMO Protocol’s open-source nature invites a similar diversity: anyone can build interfaces or tools on top of it, creating a competitive, decentralized advertising ecosystem rather than a walled garden. * Decentralized Transactions: Ulbricht’s DSP implied decentralized mechanisms for value exchange. NextBlock delivers this through the Bitcoin Lightning Network, ensuring that payments for ads are secure, instantaneous and final, a practical realization of Ulbricht’s call for user-controlled value flows. * Privacy and Control: While Ulbricht emphasized privacy in social interactions, the PROMO Protocol is public by default. Individuals are fully aware of all data that they generate since all Nostr messages are signed. All participants interact directly via Nostr.
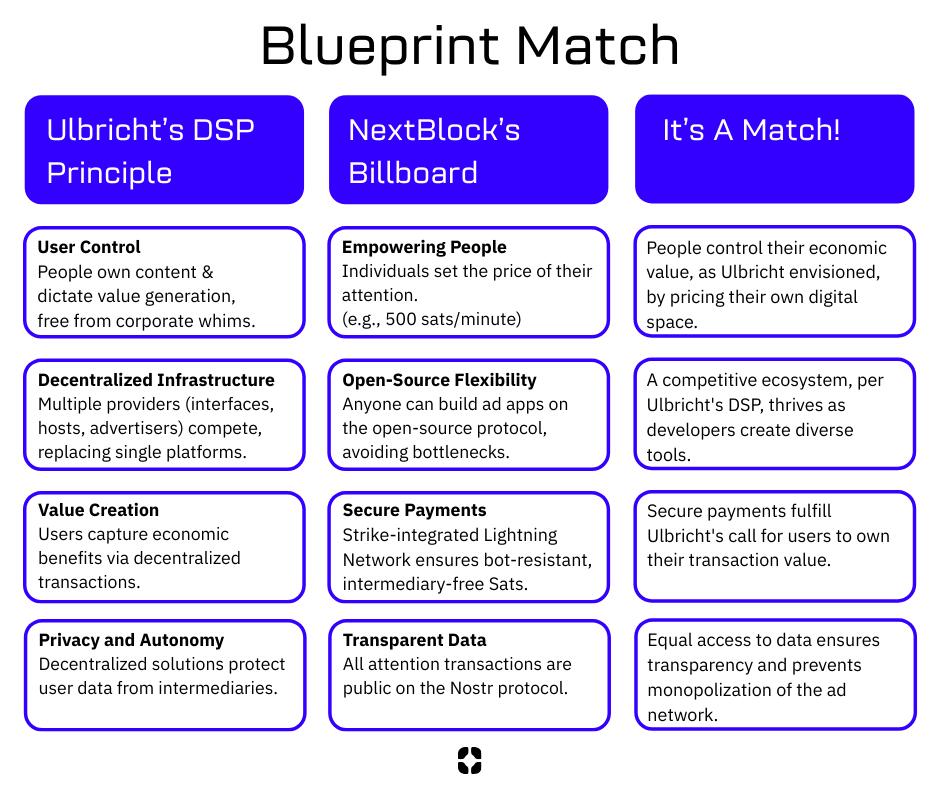 [Blueprint Match, source NextBlock]
[Blueprint Match, source NextBlock]
Who We Are
NextBlock is a US-based new media company reimagining digital ads for a decentralized future. Our founders, software and strategy experts, were hobbyist podcasters struggling to promote their work online without gaming the system. That sparked an idea: using new tech like Nostr and Bitcoin to build a decentralized attention market for people who value control and businesses seeking real connections.
Our first product, Billboard, is launching this June.
Open for All
Our model’s open-source! Check out the PROMO Protocol, built for promotion and attention trading. Anyone can join this decentralized ad network. Run your own billboard or use ours. This is a growing ecosystem for a new ad economy.
Our Vision
NextBlock wants to help build a new decentralized internet. Our revolutionary and transparent business model will bring honest revenue to companies hosting valuable digital spaces. Together, we will discover what our attention is really worth.
Read our Manifesto to learn more.
NextBlock is registered in Texas, USA.
-
 @ 975e4ad5:8d4847ce
2025-05-16 11:22:20
@ 975e4ad5:8d4847ce
2025-05-16 11:22:20Introduction
Bitcoin and torrents are two technologies that have reshaped how people share information and resources in the digital age. Both are built on decentralized principles and challenge traditional systems—torrents in the realm of file sharing, and Bitcoin in the world of finance. However, while torrents have seen a decline in popularity with the rise of streaming platforms like Netflix and HBO, many wonder whether Bitcoin will follow a similar trajectory or continue to grow as a widely adopted technology. This article explores the similarities between the two technologies, the resilience of torrents against attempts to shut them down, the reasons for their declining popularity, and why Bitcoin is likely to avoid a similar fate.
Similarities Between Torrents and Bitcoin
Torrents and Bitcoin share several key characteristics that make them unique and resilient:
-
Decentralization:\ Torrents rely on peer-to-peer (P2P) networks, where users share files directly with each other without depending on a central server. Similarly, Bitcoin operates on a blockchain—a decentralized network of nodes that maintain and validate transactions. This lack of a central authority makes both technologies difficult to control or shut down.
-
Censorship Resistance:\ Both systems are designed to withstand attempts at restriction. Torrents continue to function even when specific sites like The Pirate Bay are blocked, as the network relies on thousands of users worldwide. Bitcoin is also resistant to government bans, as transactions are processed by a global network of miners.
-
Anonymity and Pseudonymity:\ Torrents allow users to share files without revealing their identities, especially when using VPNs. Bitcoin, while pseudonymous (transactions are public but not directly tied to real-world identities), offers a similar level of privacy, attracting users seeking financial freedom.
-
Open Source:\ Both technologies are open-source, enabling developers to improve and adapt them. This fosters innovation and makes the systems more resilient to attacks.
Why Torrents Cannot Be Stopped
Torrents have persisted despite numerous attempts to curb them due to their decentralized nature. Governments and organizations have shut down sites like The Pirate Bay and Kickass Torrents, but new platforms quickly emerge. The key reasons for their resilience include:
-
P2P Architecture:\ Torrents do not rely on a single server. Every user downloading or sharing a file becomes part of the network, making it impossible to completely dismantle.
-
Global Distribution:\ Millions of users worldwide sustain torrent networks. Even if one country imposes strict regulations, others continue to support the system.
-
Adaptability:\ The torrent community quickly adapts to challenges, using VPNs, proxy servers, or the dark web to bypass restrictions.
Despite this resilience, the popularity of torrents has significantly declined in recent years, particularly among younger users.
The Decline of Torrents: Why They Lost Popularity
In the early 2000s, torrents were the primary way to access movies, music, and software. They were easy to use, free, and offered a vast array of content. However, the rise of streaming platforms like Netflix, HBO, Disney+, and Spotify has changed how people consume media. The main reasons for the decline of torrents include:
-
Convenience:\ Streaming platforms provide instant access to high-quality content without the need for downloading or specialized software. Torrents, in contrast, require technical knowledge and are often slower.
-
Legality and Safety:\ Using torrents carries risks such as viruses, malware, and legal consequences. Streaming services offer a safe and legal alternative.
-
Marketing and Accessibility:\ Platforms like Netflix invest billions in original content and marketing, attracting younger users who prefer easy access over free but risky downloads.
-
Social Shifts:\ Younger generations, raised with access to subscription services, are often unfamiliar with torrents or view them as outdated. Studies from 2023 indicate that only a small percentage of people under 25 regularly use torrents.
Despite this decline, torrents have not disappeared entirely. They are still used in regions with limited access to streaming services or by users who value free access to niche content.
Why Bitcoin Will Not Share the Fate of Torrents
Despite the similarities, Bitcoin has unique characteristics that make it more likely to achieve mainstream adoption rather than being overshadowed by alternatives. Here are the key reasons:
-
Financial Revolution:\ Bitcoin addresses problems that lack direct alternatives. It enables transactions without intermediaries, which is particularly valuable in countries with unstable currencies or limited banking access. Unlike torrents, which were replaced by more convenient streaming platforms, traditional financial systems still have flaws that Bitcoin addresses.
-
Institutional Adoption:\ Major companies like Tesla, PayPal, and Square accept Bitcoin or invest in it. Financial institutions, including JPMorgan and Goldman Sachs, are developing cryptocurrency-related products. This institutional acceptance boosts Bitcoin’s credibility and legitimacy, something torrents never achieved.
-
Limited Supply:\ Bitcoin’s fixed supply of 21 million coins makes it attractive as a store of value, similar to gold. This characteristic distinguishes it from other technologies and gives it potential for long-term growth.
-
Technological Advancements:\ The Bitcoin network evolves through improvements like the Lightning Network, which makes transactions faster and cheaper. These innovations make it competitive with traditional payment systems, whereas torrents failed to adapt to streaming technologies.
-
Global Financial Integration:\ Unlike torrents, which remained in the niche of file sharing, Bitcoin has the potential to integrate into the global financial system. Countries like El Salvador have already recognized it as legal tender, and others may follow suit.
-
Cultural and Economic Significance:\ Bitcoin is perceived not only as a technology but also as a movement for financial independence and decentralization. This ideology attracts young people and tech enthusiasts, making it more resilient to the social shifts that affected torrents.
Conclusion
Torrents and Bitcoin share common roots as decentralized technologies that challenge the status quo. However, while torrents lost popularity due to the rise of more convenient and legal alternatives, Bitcoin has the potential to avoid this fate. Its ability to address real financial problems, institutional adoption, and technological advancements make it a likely candidate for mainstream use in the future. While torrents remained a niche technology, Bitcoin is emerging as a global force that could transform how the world perceives money.
-
-
 @ 9bde4214:06ca052b
2025-04-22 18:13:37
@ 9bde4214:06ca052b
2025-04-22 18:13:37"It's gonna be permissionless or hell."
Gigi and gzuuus are vibing towards dystopia.
Books & articles mentioned:
- AI 2027
- DVMs were a mistake
- Careless People by Sarah Wynn-Williams
- Takedown by Laila michelwait
- The Ultimate Resource by Julian L. Simon
- Harry Potter by J.K. Rowling
- Momo by Michael Ende
In this dialogue:
- Pablo's Roo Setup
- Tech Hype Cycles
- AI 2027
- Prompt injection and other attacks
- Goose and DVMCP
- Cursor vs Roo Code
- Staying in control thanks to Amber and signing delegation
- Is YOLO mode here to stay?
- What agents to trust?
- What MCP tools to trust?
- What code snippets to trust?
- Everyone will run into the issues of trust and micropayments
- Nostr solves Web of Trust & micropayments natively
- Minimalistic & open usually wins
- DVMCP exists thanks to Totem
- Relays as Tamagochis
- Agents aren't nostr experts, at least not right now
- Fix a mistake once & it's fixed forever
- Giving long-term memory to LLMs
- RAG Databases signed by domain experts
- Human-agent hybrids & Chess
- Nostr beating heart
- Pluggable context & experts
- "You never need an API key for anything"
- Sats and social signaling
- Difficulty-adjusted PoW as a rare-limiting mechanism
- Certificate authorities and centralization
- No solutions to policing speech!
- OAuth and how it centralized
- Login with nostr
- Closed vs open-source models
- Tiny models vs large models
- The minions protocol (Stanford paper)
- Generalist models vs specialized models
- Local compute & encrypted queries
- Blinded compute
- "In the eyes of the state, agents aren't people"
- Agents need identity and money; nostr provides both
- "It's gonna be permissionless or hell"
- We already have marketplaces for MCP stuff, code snippets, and other things
- Most great stuff came from marketplaces (browsers, games, etc)
- Zapstore shows that this is already working
- At scale, central control never works. There's plenty scams and viruses in the app stores.
- Using nostr to archive your user-generated content
- HAVEN, blossom, novia
- The switcharoo from advertisements to training data
- What is Truth?
- What is Real?
- "We're vibing into dystopia"
- Who should be the arbiter of Truth?
- First Amendment & why the Logos is sacred
- Silicon Valley AI bros arrogantly dismiss wisdom and philosophy
- Suicide rates & the meaning crisis
- Are LLMs symbiotic or parasitic?
- The Amish got it right
- Are we gonna make it?
- Careless People by Sarah Wynn-Williams
- Takedown by Laila michelwait
- Harry Potter dementors & Momo's time thieves
- Facebook & Google as non-human (superhuman) agents
- Zapping as a conscious action
- Privacy and the internet
- Plausible deniability thanks to generative models
- Google glasses, glassholes, and Meta's Ray Ben's
- People crave realness
- Bitcoin is the realest money we ever had
- Nostr allows for real and honest expression
- How do we find out what's real?
- Constraints, policing, and chilling effects
- Jesus' plans for DVMCP
- Hzrd's article on how DVMs are broken (DVMs were a mistake)
- Don't believe the hype
- DVMs pre-date MCP tools
- Data Vending Machines were supposed to be stupid: put coin in, get stuff out.
- Self-healing vibe-coding
- IP addresses as scarce assets
- Atomic swaps and the ASS protocol
- More marketplaces, less silos
- The intensity of #SovEng and the last 6 weeks
- If you can vibe-code everything, why build anything?
- Time, the ultimate resource
- What are the LLMs allowed to think?
- Natural language interfaces are inherently dialogical
- Sovereign Engineering is dialogical too
-
 @ a39d19ec:3d88f61e
2025-04-22 12:44:42
@ a39d19ec:3d88f61e
2025-04-22 12:44:42Die Debatte um Migration, Grenzsicherung und Abschiebungen wird in Deutschland meist emotional geführt. Wer fordert, dass illegale Einwanderer abgeschoben werden, sieht sich nicht selten dem Vorwurf des Rassismus ausgesetzt. Doch dieser Vorwurf ist nicht nur sachlich unbegründet, sondern verkehrt die Realität ins Gegenteil: Tatsächlich sind es gerade diejenigen, die hinter jeder Forderung nach Rechtssicherheit eine rassistische Motivation vermuten, die selbst in erster Linie nach Hautfarbe, Herkunft oder Nationalität urteilen.
Das Recht steht über Emotionen
Deutschland ist ein Rechtsstaat. Das bedeutet, dass Regeln nicht nach Bauchgefühl oder politischer Stimmungslage ausgelegt werden können, sondern auf klaren gesetzlichen Grundlagen beruhen müssen. Einer dieser Grundsätze ist in Artikel 16a des Grundgesetzes verankert. Dort heißt es:
„Auf Absatz 1 [Asylrecht] kann sich nicht berufen, wer aus einem Mitgliedstaat der Europäischen Gemeinschaften oder aus einem anderen Drittstaat einreist, in dem die Anwendung des Abkommens über die Rechtsstellung der Flüchtlinge und der Europäischen Menschenrechtskonvention sichergestellt ist.“
Das bedeutet, dass jeder, der über sichere Drittstaaten nach Deutschland einreist, keinen Anspruch auf Asyl hat. Wer dennoch bleibt, hält sich illegal im Land auf und unterliegt den geltenden Regelungen zur Rückführung. Die Forderung nach Abschiebungen ist daher nichts anderes als die Forderung nach der Einhaltung von Recht und Gesetz.
Die Umkehrung des Rassismusbegriffs
Wer einerseits behauptet, dass das deutsche Asyl- und Aufenthaltsrecht strikt durchgesetzt werden soll, und andererseits nicht nach Herkunft oder Hautfarbe unterscheidet, handelt wertneutral. Diejenigen jedoch, die in einer solchen Forderung nach Rechtsstaatlichkeit einen rassistischen Unterton sehen, projizieren ihre eigenen Denkmuster auf andere: Sie unterstellen, dass die Debatte ausschließlich entlang ethnischer, rassistischer oder nationaler Kriterien geführt wird – und genau das ist eine rassistische Denkweise.
Jemand, der illegale Einwanderung kritisiert, tut dies nicht, weil ihn die Herkunft der Menschen interessiert, sondern weil er den Rechtsstaat respektiert. Hingegen erkennt jemand, der hinter dieser Kritik Rassismus wittert, offenbar in erster Linie die „Rasse“ oder Herkunft der betreffenden Personen und reduziert sie darauf.
Finanzielle Belastung statt ideologischer Debatte
Neben der rechtlichen gibt es auch eine ökonomische Komponente. Der deutsche Wohlfahrtsstaat basiert auf einem Solidarprinzip: Die Bürger zahlen in das System ein, um sich gegenseitig in schwierigen Zeiten zu unterstützen. Dieser Wohlstand wurde über Generationen hinweg von denjenigen erarbeitet, die hier seit langem leben. Die Priorität liegt daher darauf, die vorhandenen Mittel zuerst unter denjenigen zu verteilen, die durch Steuern, Sozialabgaben und Arbeit zum Erhalt dieses Systems beitragen – nicht unter denen, die sich durch illegale Einreise und fehlende wirtschaftliche Eigenleistung in das System begeben.
Das ist keine ideologische Frage, sondern eine rein wirtschaftliche Abwägung. Ein Sozialsystem kann nur dann nachhaltig funktionieren, wenn es nicht unbegrenzt belastet wird. Würde Deutschland keine klaren Regeln zur Einwanderung und Abschiebung haben, würde dies unweigerlich zur Überlastung des Sozialstaates führen – mit negativen Konsequenzen für alle.
Sozialpatriotismus
Ein weiterer wichtiger Aspekt ist der Schutz der Arbeitsleistung jener Generationen, die Deutschland nach dem Zweiten Weltkrieg mühsam wieder aufgebaut haben. Während oft betont wird, dass die Deutschen moralisch kein Erbe aus der Zeit vor 1945 beanspruchen dürfen – außer der Verantwortung für den Holocaust –, ist es umso bedeutsamer, das neue Erbe nach 1945 zu respektieren, das auf Fleiß, Disziplin und harter Arbeit beruht. Der Wiederaufbau war eine kollektive Leistung deutscher Menschen, deren Früchte nicht bedenkenlos verteilt werden dürfen, sondern vorrangig denjenigen zugutekommen sollten, die dieses Fundament mitgeschaffen oder es über Generationen mitgetragen haben.
Rechtstaatlichkeit ist nicht verhandelbar
Wer sich für eine konsequente Abschiebepraxis ausspricht, tut dies nicht aus rassistischen Motiven, sondern aus Respekt vor der Rechtsstaatlichkeit und den wirtschaftlichen Grundlagen des Landes. Der Vorwurf des Rassismus in diesem Kontext ist daher nicht nur falsch, sondern entlarvt eine selektive Wahrnehmung nach rassistischen Merkmalen bei denjenigen, die ihn erheben.
-
 @ 4ba8e86d:89d32de4
2025-04-21 02:13:56
@ 4ba8e86d:89d32de4
2025-04-21 02:13:56Tutorial feito por nostr:nostr:npub1rc56x0ek0dd303eph523g3chm0wmrs5wdk6vs0ehd0m5fn8t7y4sqra3tk poste original abaixo:
Parte 1 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/263585/tutorial-debloat-de-celulares-android-via-adb-parte-1
Parte 2 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/index.php/263586/tutorial-debloat-de-celulares-android-via-adb-parte-2
Quando o assunto é privacidade em celulares, uma das medidas comumente mencionadas é a remoção de bloatwares do dispositivo, também chamado de debloat. O meio mais eficiente para isso sem dúvidas é a troca de sistema operacional. Custom Rom’s como LineageOS, GrapheneOS, Iodé, CalyxOS, etc, já são bastante enxutos nesse quesito, principalmente quanto não é instalado os G-Apps com o sistema. No entanto, essa prática pode acabar resultando em problemas indesejados como a perca de funções do dispositivo, e até mesmo incompatibilidade com apps bancários, tornando este método mais atrativo para quem possui mais de um dispositivo e separando um apenas para privacidade. Pensando nisso, pessoas que possuem apenas um único dispositivo móvel, que são necessitadas desses apps ou funções, mas, ao mesmo tempo, tem essa visão em prol da privacidade, buscam por um meio-termo entre manter a Stock rom, e não ter seus dados coletados por esses bloatwares. Felizmente, a remoção de bloatwares é possível e pode ser realizada via root, ou mais da maneira que este artigo irá tratar, via adb.
O que são bloatwares?
Bloatware é a junção das palavras bloat (inchar) + software (programa), ou seja, um bloatware é basicamente um programa inútil ou facilmente substituível — colocado em seu dispositivo previamente pela fabricante e operadora — que está no seu dispositivo apenas ocupando espaço de armazenamento, consumindo memória RAM e pior, coletando seus dados e enviando para servidores externos, além de serem mais pontos de vulnerabilidades.
O que é o adb?
O Android Debug Brigde, ou apenas adb, é uma ferramenta que se utiliza das permissões de usuário shell e permite o envio de comandos vindo de um computador para um dispositivo Android exigindo apenas que a depuração USB esteja ativa, mas também pode ser usada diretamente no celular a partir do Android 11, com o uso do Termux e a depuração sem fio (ou depuração wifi). A ferramenta funciona normalmente em dispositivos sem root, e também funciona caso o celular esteja em Recovery Mode.
Requisitos:
Para computadores:
• Depuração USB ativa no celular; • Computador com adb; • Cabo USB;
Para celulares:
• Depuração sem fio (ou depuração wifi) ativa no celular; • Termux; • Android 11 ou superior;
Para ambos:
• Firewall NetGuard instalado e configurado no celular; • Lista de bloatwares para seu dispositivo;
Ativação de depuração:
Para ativar a Depuração USB em seu dispositivo, pesquise como ativar as opções de desenvolvedor de seu dispositivo, e lá ative a depuração. No caso da depuração sem fio, sua ativação irá ser necessária apenas no momento que for conectar o dispositivo ao Termux.
Instalação e configuração do NetGuard
O NetGuard pode ser instalado através da própria Google Play Store, mas de preferência instale pela F-Droid ou Github para evitar telemetria.
F-Droid: https://f-droid.org/packages/eu.faircode.netguard/
Github: https://github.com/M66B/NetGuard/releases
Após instalado, configure da seguinte maneira:
Configurações → padrões (lista branca/negra) → ative as 3 primeiras opções (bloquear wifi, bloquear dados móveis e aplicar regras ‘quando tela estiver ligada’);
Configurações → opções avançadas → ative as duas primeiras (administrar aplicativos do sistema e registrar acesso a internet);
Com isso, todos os apps estarão sendo bloqueados de acessar a internet, seja por wifi ou dados móveis, e na página principal do app basta permitir o acesso a rede para os apps que você vai usar (se necessário). Permita que o app rode em segundo plano sem restrição da otimização de bateria, assim quando o celular ligar, ele já estará ativo.
Lista de bloatwares
Nem todos os bloatwares são genéricos, haverá bloatwares diferentes conforme a marca, modelo, versão do Android, e até mesmo região.
Para obter uma lista de bloatwares de seu dispositivo, caso seu aparelho já possua um tempo de existência, você encontrará listas prontas facilmente apenas pesquisando por elas. Supondo que temos um Samsung Galaxy Note 10 Plus em mãos, basta pesquisar em seu motor de busca por:
Samsung Galaxy Note 10 Plus bloatware listProvavelmente essas listas já terão inclusas todos os bloatwares das mais diversas regiões, lhe poupando o trabalho de buscar por alguma lista mais específica.
Caso seu aparelho seja muito recente, e/ou não encontre uma lista pronta de bloatwares, devo dizer que você acaba de pegar em merda, pois é chato para um caralho pesquisar por cada aplicação para saber sua função, se é essencial para o sistema ou se é facilmente substituível.
De antemão já aviso, que mais para frente, caso vossa gostosura remova um desses aplicativos que era essencial para o sistema sem saber, vai acabar resultando na perda de alguma função importante, ou pior, ao reiniciar o aparelho o sistema pode estar quebrado, lhe obrigando a seguir com uma formatação, e repetir todo o processo novamente.
Download do adb em computadores
Para usar a ferramenta do adb em computadores, basta baixar o pacote chamado SDK platform-tools, disponível através deste link: https://developer.android.com/tools/releases/platform-tools. Por ele, você consegue o download para Windows, Mac e Linux.
Uma vez baixado, basta extrair o arquivo zipado, contendo dentro dele uma pasta chamada platform-tools que basta ser aberta no terminal para se usar o adb.
Download do adb em celulares com Termux.
Para usar a ferramenta do adb diretamente no celular, antes temos que baixar o app Termux, que é um emulador de terminal linux, e já possui o adb em seu repositório. Você encontra o app na Google Play Store, mas novamente recomendo baixar pela F-Droid ou diretamente no Github do projeto.
F-Droid: https://f-droid.org/en/packages/com.termux/
Github: https://github.com/termux/termux-app/releases
Processo de debloat
Antes de iniciarmos, é importante deixar claro que não é para você sair removendo todos os bloatwares de cara sem mais nem menos, afinal alguns deles precisam antes ser substituídos, podem ser essenciais para você para alguma atividade ou função, ou até mesmo são insubstituíveis.
Alguns exemplos de bloatwares que a substituição é necessária antes da remoção, é o Launcher, afinal, é a interface gráfica do sistema, e o teclado, que sem ele só é possível digitar com teclado externo. O Launcher e teclado podem ser substituídos por quaisquer outros, minha recomendação pessoal é por aqueles que respeitam sua privacidade, como Pie Launcher e Simple Laucher, enquanto o teclado pelo OpenBoard e FlorisBoard, todos open-source e disponíveis da F-Droid.
Identifique entre a lista de bloatwares, quais você gosta, precisa ou prefere não substituir, de maneira alguma você é obrigado a remover todos os bloatwares possíveis, modifique seu sistema a seu bel-prazer. O NetGuard lista todos os apps do celular com o nome do pacote, com isso você pode filtrar bem qual deles não remover.
Um exemplo claro de bloatware insubstituível e, portanto, não pode ser removido, é o com.android.mtp, um protocolo onde sua função é auxiliar a comunicação do dispositivo com um computador via USB, mas por algum motivo, tem acesso a rede e se comunica frequentemente com servidores externos. Para esses casos, e melhor solução mesmo é bloquear o acesso a rede desses bloatwares com o NetGuard.
MTP tentando comunicação com servidores externos:
Executando o adb shell
No computador
Faça backup de todos os seus arquivos importantes para algum armazenamento externo, e formate seu celular com o hard reset. Após a formatação, e a ativação da depuração USB, conecte seu aparelho e o pc com o auxílio de um cabo USB. Muito provavelmente seu dispositivo irá apenas começar a carregar, por isso permita a transferência de dados, para que o computador consiga se comunicar normalmente com o celular.
Já no pc, abra a pasta platform-tools dentro do terminal, e execute o seguinte comando:
./adb start-serverO resultado deve ser:
daemon not running; starting now at tcp:5037 daemon started successfully
E caso não apareça nada, execute:
./adb kill-serverE inicie novamente.
Com o adb conectado ao celular, execute:
./adb shellPara poder executar comandos diretamente para o dispositivo. No meu caso, meu celular é um Redmi Note 8 Pro, codinome Begonia.
Logo o resultado deve ser:
begonia:/ $
Caso ocorra algum erro do tipo:
adb: device unauthorized. This adb server’s $ADB_VENDOR_KEYS is not set Try ‘adb kill-server’ if that seems wrong. Otherwise check for a confirmation dialog on your device.
Verifique no celular se apareceu alguma confirmação para autorizar a depuração USB, caso sim, autorize e tente novamente. Caso não apareça nada, execute o kill-server e repita o processo.
No celular
Após realizar o mesmo processo de backup e hard reset citado anteriormente, instale o Termux e, com ele iniciado, execute o comando:
pkg install android-toolsQuando surgir a mensagem “Do you want to continue? [Y/n]”, basta dar enter novamente que já aceita e finaliza a instalação
Agora, vá até as opções de desenvolvedor, e ative a depuração sem fio. Dentro das opções da depuração sem fio, terá uma opção de emparelhamento do dispositivo com um código, que irá informar para você um código em emparelhamento, com um endereço IP e porta, que será usado para a conexão com o Termux.
Para facilitar o processo, recomendo que abra tanto as configurações quanto o Termux ao mesmo tempo, e divida a tela com os dois app’s, como da maneira a seguir:
Para parear o Termux com o dispositivo, não é necessário digitar o ip informado, basta trocar por “localhost”, já a porta e o código de emparelhamento, deve ser digitado exatamente como informado. Execute:
adb pair localhost:porta CódigoDeEmparelhamentoDe acordo com a imagem mostrada anteriormente, o comando ficaria “adb pair localhost:41255 757495”.
Com o dispositivo emparelhado com o Termux, agora basta conectar para conseguir executar os comandos, para isso execute:
adb connect localhost:portaObs: a porta que você deve informar neste comando não é a mesma informada com o código de emparelhamento, e sim a informada na tela principal da depuração sem fio.
Pronto! Termux e adb conectado com sucesso ao dispositivo, agora basta executar normalmente o adb shell:
adb shellRemoção na prática Com o adb shell executado, você está pronto para remover os bloatwares. No meu caso, irei mostrar apenas a remoção de um app (Google Maps), já que o comando é o mesmo para qualquer outro, mudando apenas o nome do pacote.
Dentro do NetGuard, verificando as informações do Google Maps:
Podemos ver que mesmo fora de uso, e com a localização do dispositivo desativado, o app está tentando loucamente se comunicar com servidores externos, e informar sabe-se lá que peste. Mas sem novidades até aqui, o mais importante é que podemos ver que o nome do pacote do Google Maps é com.google.android.apps.maps, e para o remover do celular, basta executar:
pm uninstall –user 0 com.google.android.apps.mapsE pronto, bloatware removido! Agora basta repetir o processo para o resto dos bloatwares, trocando apenas o nome do pacote.
Para acelerar o processo, você pode já criar uma lista do bloco de notas com os comandos, e quando colar no terminal, irá executar um atrás do outro.
Exemplo de lista:
Caso a donzela tenha removido alguma coisa sem querer, também é possível recuperar o pacote com o comando:
cmd package install-existing nome.do.pacotePós-debloat
Após limpar o máximo possível o seu sistema, reinicie o aparelho, caso entre no como recovery e não seja possível dar reboot, significa que você removeu algum app “essencial” para o sistema, e terá que formatar o aparelho e repetir toda a remoção novamente, desta vez removendo poucos bloatwares de uma vez, e reiniciando o aparelho até descobrir qual deles não pode ser removido. Sim, dá trabalho… quem mandou querer privacidade?
Caso o aparelho reinicie normalmente após a remoção, parabéns, agora basta usar seu celular como bem entender! Mantenha o NetGuard sempre executando e os bloatwares que não foram possíveis remover não irão se comunicar com servidores externos, passe a usar apps open source da F-Droid e instale outros apps através da Aurora Store ao invés da Google Play Store.
Referências: Caso você seja um Australopithecus e tenha achado este guia difícil, eis uma videoaula (3:14:40) do Anderson do canal Ciberdef, realizando todo o processo: http://odysee.com/@zai:5/Como-remover-at%C3%A9-200-APLICATIVOS-que-colocam-a-sua-PRIVACIDADE-E-SEGURAN%C3%87A-em-risco.:4?lid=6d50f40314eee7e2f218536d9e5d300290931d23
Pdf’s do Anderson citados na videoaula: créditos ao anon6837264 http://eternalcbrzpicytj4zyguygpmkjlkddxob7tptlr25cdipe5svyqoqd.onion/file/3863a834d29285d397b73a4af6fb1bbe67c888d72d30/t-05e63192d02ffd.pdf
Processo de instalação do Termux e adb no celular: https://youtu.be/APolZrPHSms
-
 @ ed5774ac:45611c5c
2025-04-19 20:29:31
@ ed5774ac:45611c5c
2025-04-19 20:29:31April 20, 2020: The day I saw my so-called friends expose themselves as gutless, brain-dead sheep.
On that day, I shared a video exposing the damning history of the Bill & Melinda Gates Foundation's vaccine campaigns in Africa and the developing world. As Gates was on every TV screen, shilling COVID jabs that didn’t even exist, I called out his blatant financial conflict of interest and pointed out the obvious in my facebook post: "Finally someone is able to explain why Bill Gates runs from TV to TV to promote vaccination. Not surprisingly, it's all about money again…" - referencing his substantial investments in vaccine technology, including BioNTech's mRNA platform that would later produce the COVID vaccines and generate massive profits for his so-called philanthropic foundation.
The conflict of interest was undeniable. I genuinely believed anyone capable of basic critical thinking would at least pause to consider these glaring financial motives. But what followed was a masterclass in human stupidity.
My facebook post from 20 April 2020:

Not only was I branded a 'conspiracy theorist' for daring to question the billionaire who stood to make a fortune off the very vaccines he was shilling, but the brain-dead, logic-free bullshit vomited by the people around me was beyond pathetic. These barely literate morons couldn’t spell "Pfizer" without auto-correct, yet they mindlessly swallowed and repeated every lie the media and government force-fed them, branding anything that cracked their fragile reality as "conspiracy theory." Big Pharma’s rap sheet—fraud, deadly cover-ups, billions in fines—could fill libraries, yet these obedient sheep didn’t bother to open a single book or read a single study before screaming their ignorance, desperate to virtue-signal their obedience. Then, like spineless lab rats, they lined up for an experimental jab rushed to the market in months, too dumb to care that proper vaccine development takes a decade.
The pathetic part is that these idiots spend hours obsessing over reviews for their useless purchases like shoes or socks, but won’t spare 60 seconds to research the experimental cocktail being injected into their veins—or even glance at the FDA’s own damning safety reports. Those same obedient sheep would read every Yelp review for a fucking coffee shop but won't spend five minutes looking up Pfizer's criminal fraud settlements. They would demand absolute obedience to ‘The Science™’—while being unable to define mRNA, explain lipid nanoparticles, or justify why trials were still running as they queued up like cattle for their jab. If they had two brain cells to rub together or spent 30 minutes actually researching, they'd know, but no—they'd rather suck down the narrative like good little slaves, too dumb to question, too weak to think.
Worst of all, they became the system’s attack dogs—not just swallowing the poison, but forcing it down others’ throats. This wasn’t ignorance. It was betrayal. They mutated into medical brownshirts, destroying lives to virtue-signal their obedience—even as their own children’s hearts swelled with inflammation.
One conversation still haunts me to this day—a masterclass in wealth-worship delusion. A close friend, as a response to my facebook post, insisted that Gates’ assumed reading list magically awards him vaccine expertise, while dismissing his billion-dollar investments in the same products as ‘no conflict of interest.’ Worse, he argued that Gates’s $5–10 billion pandemic windfall was ‘deserved.’
This exchange crystallizes civilization’s intellectual surrender: reason discarded with religious fervor, replaced by blind faith in corporate propaganda.
The comment of a friend on my facebook post that still haunts me to this day:

Walking Away from the Herd
After a period of anger and disillusionment, I made a decision: I would no longer waste energy arguing with people who refused to think for themselves. If my circle couldn’t even ask basic questions—like why an untested medical intervention was being pushed with unprecedented urgency—then I needed a new community.
Fortunately, I already knew where to look. For three years, I had been involved in Bitcoin, a space where skepticism wasn’t just tolerated—it was demanded. Here, I’d met some of the most principled and independent thinkers I’d ever encountered. These were people who understood the corrupting influence of centralized power—whether in money, media, or politics—and who valued sovereignty, skepticism, and integrity. Instead of blind trust, bitcoiners practiced relentless verification. And instead of empty rhetoric, they lived by a simple creed: Don’t trust. Verify.
It wasn’t just a philosophy. It was a lifeline. So I chose my side and I walked away from the herd.
Finding My Tribe
Over the next four years, I immersed myself in Bitcoin conferences, meetups, and spaces where ideas were tested, not parroted. Here, I encountered extraordinary people: not only did they share my skepticism toward broken systems, but they challenged me to sharpen it.
No longer adrift in a sea of mindless conformity, I’d found a crew of thinkers who cut through the noise. They saw clearly what most ignored—that at the core of society’s collapse lay broken money, the silent tax on time, freedom, and truth itself. But unlike the complainers I’d left behind, these people built. They coded. They wrote. They risked careers and reputations to expose the rot. Some faced censorship; others, mockery. All understood the stakes.
These weren’t keyboard philosophers. They were modern-day Cassandras, warning of inflation’s theft, the Fed’s lies, and the coming dollar collapse—not for clout, but because they refused to kneel to a dying regime. And in their defiance, I found something rare: a tribe that didn’t just believe in a freer future. They were engineering it.
April 20, 2024: No more herd. No more lies. Only proof-of-work.
On April 20, 2024, exactly four years after my last Facebook post, the one that severed my ties to the herd for good—I stood in front of Warsaw’s iconic Palace of Culture and Science, surrounded by 400 bitcoiners who felt like family. We were there to celebrate Bitcoin’s fourth halving, but it was more than a protocol milestone. It was a reunion of sovereign individuals. Some faces I’d known since the early days; others, I’d met only hours before. We bonded instantly—heated debates, roaring laughter, zero filters on truths or on so called conspiracy theories.
As the countdown to the halving began, it hit me: This was the antithesis of the hollow world I’d left behind. No performative outrage, no coerced consensus—just a room of unyielding minds who’d traded the illusion of safety for the grit of truth. Four years prior, I’d been alone in my resistance. Now, I raised my glass among my people - those who had seen the system's lies and chosen freedom instead. Each had their own story of awakening, their own battles fought, but here we shared the same hard-won truth.
The energy wasn’t just electric. It was alive—the kind that emerges when free people build rather than beg. For the first time, I didn’t just belong. I was home. And in that moment, the halving’s ticking clock mirrored my own journey: cyclical, predictable in its scarcity, revolutionary in its consequences. Four years had burned away the old world. What remained was stronger.

No Regrets
Leaving the herd wasn’t a choice—it was evolution. My soul shouted: "I’d rather stand alone than kneel with the masses!". The Bitcoin community became more than family; they’re living proof that the world still produces warriors, not sheep. Here, among those who forge truth, I found something extinct elsewhere: hope that burns brighter with every halving, every block, every defiant mind that joins the fight.
Change doesn’t come from the crowd. It starts when one person stops applauding.
Today, I stand exactly where I always wanted to be—shoulder-to-shoulder with my true family: the rebels, the builders, the ungovernable. Together, we’re building the decentralized future.
-
 @ 6e0ea5d6:0327f353
2025-04-19 15:09:18
@ 6e0ea5d6:0327f353
2025-04-19 15:09:18🩸
The world won’t stop and wait for you to recover.Do your duty regardless of how you feel. That’s the only guarantee you’ll end the day alright.
You’ve heard it before: “The worst workout is the one you didn’t do.” Sometimes you don’t feel like going to the gym. You start bargaining with laziness: “I didn’t sleep well… maybe I should skip today.” But then you go anyway, committing only to the bare minimum your energy allows. And once you start, your body outperforms your mind’s assumptions—it turns out to be one of the best workouts you’ve had in a long time. The feeling of following through, of winning a battle you were losing, gives you the confidence to own the rest of your day. You finally feel good.
And that wouldn’t have happened if you stayed home waiting to feel better. Guilt would’ve joined forces with discouragement, and you’d be crushed by melancholy in a victim mindset. That loss would bleed into the rest of your week, conditioning your mind: because you didn’t spend your energy on the workout, you’d stay up late, wake up worse, and while waiting to feel “ready,” you’d lose a habit that took months of effort to build.
When in doubt, just do your duty. Stick to the plan. Don’t negotiate with your feelings—outsmart them. “Just one page today,” and you’ll end up reading ten. “Only the easy tasks,” and you’ll gain momentum to conquer the hard ones. Laziness is a serpent—you win when you make no deals with it.
A close friend once told me that when he was at his limit during a second job shift, he’d open a picture on his phone—of a fridge or a stove he needed to buy for his home—and that image gave him strength to stay awake. That moment stuck with me forever.
Do you really think the world will have the same mercy on you that you have on yourself? Don’t be surprised when it doesn’t spare you. Move forward even while stitching your wounds: “If you wait for perfect conditions, you’ll never do anything.” (Ecclesiastes 11:4)
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 6e0ea5d6:0327f353
2025-04-19 15:02:55
@ 6e0ea5d6:0327f353
2025-04-19 15:02:55My friend, let yourself be deluded for a moment, and reality will see to it that your fantasy is shattered—like a hammer crushing marble. The real world grants no mercy; it will relentlessly tear down your aspirations, casting them into the abyss of disillusionment and burying your dreams under the unbearable weight of your own expectations. It’s an inescapable fate—but the outcome is still in your hands: perish at the bottom like a wretch or turn the pit into a trench.
Davvero, everyone must eventually face something that breaks them. It is in devastation that man discovers what he is made of, and in the silence of defeat that he hears the finest advice. Yet the weak would rather embrace the convenient lie of self-pity, blaming life for failures that are, in truth, the result of their own negligence and cowardly choices. If you hide behind excuses because you fear the painful truth, know this: the responsibility has always been yours.
Ascolta bene! Just remain steadfast, even when everything feels like an endless maze. The difficulties you face today—those you believe you’ll never overcome—will one day seem insignificant under the light of time and experience. Tomorrow, you’ll look back and laugh at yourself for ever letting these storms seem so overwhelming.
Now, it’s up to you to fight your own battle—for the evil day spares no one. Don’t let yourself be paralyzed by shock or bow before adversity. Be strong and of good courage—not as one who waits for relief, but as one prepared to face the inevitable and turn pain into glory.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 3ffac3a6:2d656657
2025-04-15 14:49:31
@ 3ffac3a6:2d656657
2025-04-15 14:49:31🏅 Como Criar um Badge Épico no Nostr com
nak+ badges.pageRequisitos:
- Ter o
nakinstalado (https://github.com/fiatjaf/nak) - Ter uma chave privada Nostr (
nsec...) - Acesso ao site https://badges.page
- Um relay ativo (ex:
wss://relay.primal.net)
🔧 Passo 1 — Criar o badge em badges.page
- Acesse o site https://badges.page
-
Clique em "New Badge" no canto superior direito
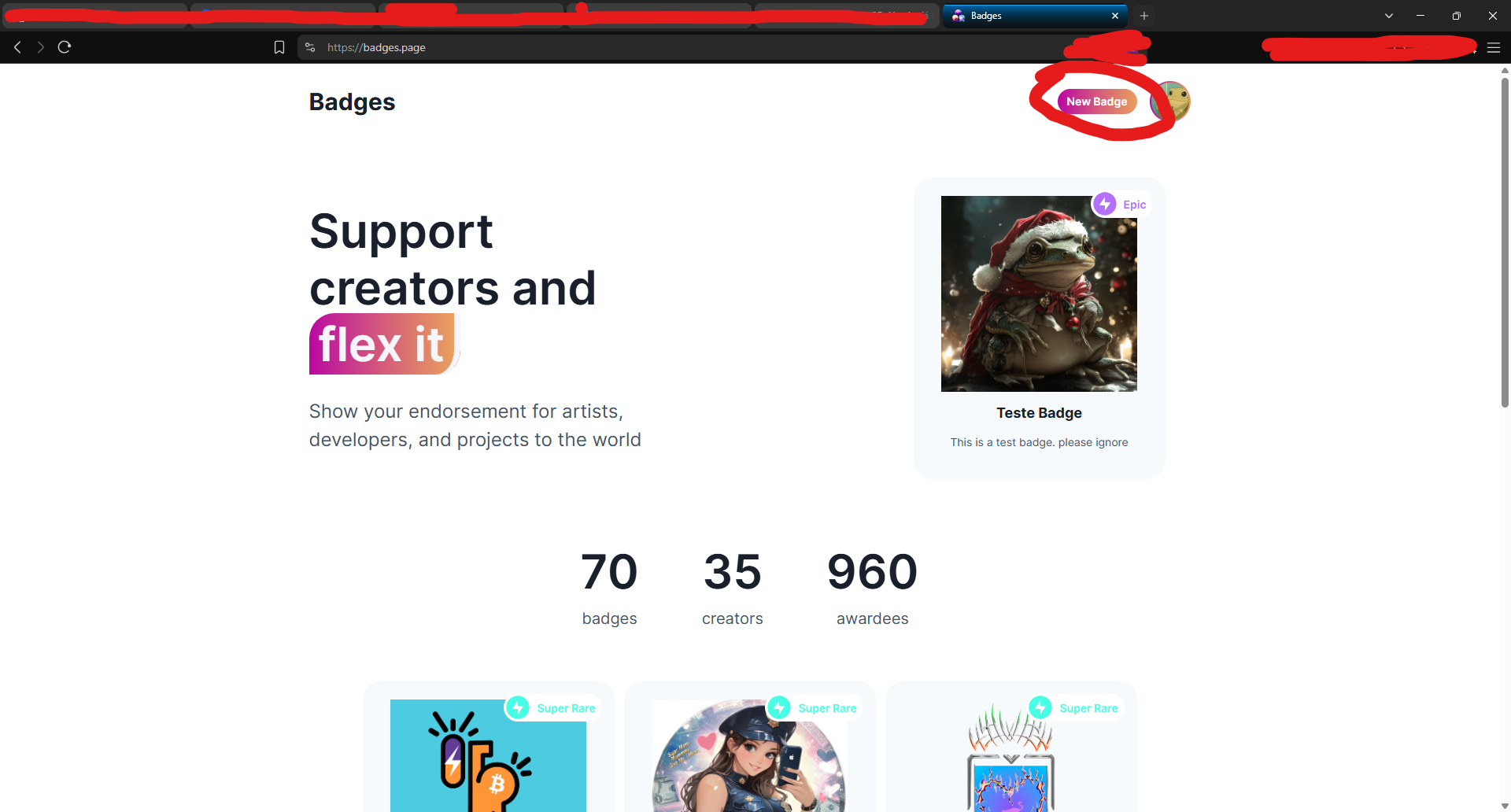
-
Preencha os campos:
- Nome (ex:
Teste Épico) - Descrição
-
Imagem e thumbnail
-
Após criar, você será redirecionado para a página do badge.
🔍 Passo 2 — Copiar o
naddrdo badgeNa barra de endereços, copie o identificador que aparece após
/a/— este é o naddr do seu badge.Exemplo:
nostr:naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0Copie:
naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0
🧠 Passo 3 — Decodificar o naddr com
nakAbra seu terminal (ou Cygwin no Windows) e rode:
bash nak decode naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0Você verá algo assim:
json { "pubkey": "3ffac3a6c859eaaa8cdddb2c7002a6e10b33efeb92d025b14ead6f8a2d656657", "kind": 30009, "identifier": "Teste-Epico" }Grave o campo
"identifier"— nesse caso: Teste-Epico
🛰️ Passo 4 — Consultar o evento no relay
Agora vamos pegar o evento do badge no relay:
bash nak req -d "Teste-Epico" wss://relay.primal.netVocê verá o conteúdo completo do evento do badge, algo assim:
json { "kind": 30009, "tags": [["d", "Teste-Epico"], ["name", "Teste Épico"], ...] }
💥 Passo 5 — Minerar o evento como "épico" (PoW 31)
Agora vem a mágica: minerar com proof-of-work (PoW 31) para que o badge seja classificado como épico!
bash nak req -d "Teste-Epico" wss://relay.primal.net | nak event --pow 31 --sec nsec1SEU_NSEC_AQUI wss://relay.primal.net wss://nos.lol wss://relay.damus.ioEsse comando: - Resgata o evento original - Gera um novo com PoW de dificuldade 31 - Assina com sua chave privada
nsec- E publica nos relays wss://relay.primal.net, wss://nos.lol e wss://relay.damus.io⚠️ Substitua
nsec1SEU_NSEC_AQUIpela sua chave privada Nostr.
✅ Resultado
Se tudo der certo, o badge será atualizado com um evento de PoW mais alto e aparecerá como "Epic" no site!
- Ter o
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 91bea5cd:1df4451c
2025-05-16 11:07:16
@ 91bea5cd:1df4451c
2025-05-16 11:07:16Instruções:
- Leia cada pergunta cuidadosamente.
- Escolha a opção (A, B, C ou D) que melhor descreve você na maioria das situações. Seja o mais honesto possível.
- Anote a letra correspondente à sua escolha para cada pergunta.
- No final, some quantas vezes você escolheu cada letra (A, B, C, D).
- Veja a seção de resultados para interpretar sua pontuação.
Teste de Temperamento
1. Em um evento social (festa, reunião), como você geralmente se comporta? A) Sou o centro das atenções, converso com todos, faço piadas e animo o ambiente. B) Tomo a iniciativa, organizo atividades ou discussões, e gosto de liderar conversas. C) Prefiro observar, conversar em grupos menores ou com pessoas que já conheço bem, e analiso o ambiente. D) Sou tranquilo, ouvinte, evito chamar atenção e me adapto ao ritmo do grupo.
2. Ao enfrentar um novo projeto ou tarefa desafiadora no trabalho ou estudo: A) Fico entusiasmado com a novidade, tenho muitas ideias iniciais, mas posso me distrair facilmente. B) Defino metas claras, crio um plano de ação rápido e foco em alcançar resultados eficientemente. C) Analiso todos os detalhes, planejo meticulosamente, prevejo possíveis problemas e busco a perfeição. D) Abordo com calma, trabalho de forma constante e organizada, e prefiro um ambiente sem pressão.
3. Como você geralmente reage a críticas? A) Tento levar na esportiva, talvez faça uma piada, mas posso me magoar momentaneamente e logo esqueço. B) Defendo meu ponto de vista vigorosamente, posso ficar irritado se sentir injustiça, mas foco em corrigir o problema. C) Levo muito a sério, analiso profundamente, posso me sentir magoado por um tempo e repenso minhas ações. D) Escuto com calma, considero a crítica objetivamente e tento não levar para o lado pessoal, buscando a paz.
4. Qual seu estilo de tomada de decisão? A) Sou impulsivo, decido rapidamente com base no entusiasmo do momento, às vezes me arrependo depois. B) Sou decidido e rápido, foco no objetivo final, às vezes sem considerar todos os detalhes ou sentimentos alheios. C) Sou ponderado, analiso todas as opções e consequências, demoro para decidir buscando a melhor escolha. D) Sou cauteloso, prefiro evitar decisões difíceis, busco consenso ou adio se possível.
5. Como você lida com rotina e repetição? A) Acho entediante rapidamente, preciso de variedade e novidade constante para me manter engajado. B) Tolero se for necessário para atingir um objetivo, mas prefiro desafios e mudanças que eu controlo. C) Aprecio a ordem e a previsibilidade, me sinto confortável com rotinas bem estabelecidas. D) Adapto-me bem à rotina, acho confortável e seguro, não gosto de mudanças bruscas.
6. Em uma discussão ou conflito: A) Tento aliviar a tensão com humor, expresso meus sentimentos abertamente, mas não guardo rancor. B) Sou direto e assertivo, defendo minha posição com firmeza, posso parecer confrontador. C) Evito confronto direto, mas fico remoendo o problema, analiso os argumentos e posso guardar ressentimento. D) Busco a conciliação, tento entender todos os lados, sou diplomático e evito o conflito a todo custo.
7. Como você expressa seus sentimentos (alegria, tristeza, raiva)? A) Expresso de forma aberta, intensa e visível, minhas emoções mudam rapidamente. B) Expresso de forma direta e forte, principalmente a raiva ou a determinação, controlo emoções "fracas". C) Tendo a internalizar, minhas emoções são profundas e duradouras, posso parecer reservado. D) Sou contido na expressão emocional, mantenho a calma externamente, mesmo que sinta algo internamente.
8. Qual seu nível de energia habitual? A) Alto, sou muito ativo, falante e entusiasmado, gosto de estar em movimento. B) Muito alto e direcionado, tenho muita energia para perseguir meus objetivos e liderar. C) Variável, posso ter picos de energia para projetos que me interessam, mas também preciso de tempo quieto para recarregar. D) Moderado e constante, sou calmo, tranquilo, prefiro atividades menos agitadas.
9. Como você organiza seu espaço de trabalho ou sua casa? A) Pode ser um pouco caótico e desorganizado, com muitas coisas interessantes espalhadas. B) Organizado de forma funcional para máxima eficiência, focado no essencial para as tarefas. C) Extremamente organizado, metódico, cada coisa em seu lugar, prezo pela ordem e estética. D) Confortável e prático, não necessariamente impecável, mas funcional e sem excessos.
10. O que mais te motiva? A) Reconhecimento social, diversão, novas experiências e interações. B) Poder, controle, desafios, alcançar metas ambiciosas e resultados concretos. C) Qualidade, significado, fazer as coisas da maneira certa, compreensão profunda. D) Paz, estabilidade, harmonia nos relacionamentos, evitar estresse e pressão.
11. Como você reage a imprevistos ou mudanças de plano? A) Adapto-me rapidamente, às vezes até gosto da novidade, embora possa atrapalhar meus planos iniciais. B) Fico irritado com a perda de controle, mas rapidamente busco uma solução alternativa para manter o objetivo. C) Sinto-me desconfortável e ansioso, preciso de tempo para reavaliar e replanejar cuidadosamente. D) Aceito com calma, sou flexível e me ajusto sem muito alarde, desde que não gere conflito.
12. Qual o seu maior medo (em termos gerais)? A) Ser rejeitado, ignorado ou ficar entediado. B) Perder o controle, parecer fraco ou incompetente. C) Cometer erros graves, ser inadequado ou imperfeito. D) Conflitos, pressão, tomar decisões erradas que afetem a estabilidade.
13. Como você costuma passar seu tempo livre? A) Socializando, saindo com amigos, buscando atividades novas e divertidas. B) Engajado em atividades produtivas, esportes competitivos, planejando próximos passos. C) Lendo, estudando, refletindo, dedicando-me a hobbies que exigem atenção e cuidado. D) Relaxando em casa, assistindo filmes, lendo tranquilamente, passando tempo com a família de forma calma.
14. Ao trabalhar em equipe: A) Sou o animador, trago ideias, conecto as pessoas, mas posso ter dificuldade em focar nos detalhes. B) Assumo a liderança naturalmente, delego tarefas, foco nos resultados e mantenho todos na linha. C) Sou o planejador e o crítico construtivo, atento aos detalhes, garanto a qualidade, mas posso ser muito exigente. D) Sou o pacificador e o colaborador, ajudo a manter a harmonia, realizo minhas tarefas de forma confiável.
15. Como você lida com prazos? A) Muitas vezes deixo para a última hora, trabalho melhor sob a pressão do prazo final, mas posso me atrapalhar. B) Gosto de terminar bem antes do prazo, vejo o prazo como um desafio a ser superado rapidamente. C) Planejo o tempo cuidadosamente para cumprir o prazo com qualidade, fico ansioso se o tempo fica curto. D) Trabalho em ritmo constante para cumprir o prazo sem estresse, não gosto de correria.
16. Qual destas frases mais te descreve? A) "A vida é uma festa!" B) "Se quer algo bem feito, faça você mesmo (ou mande fazer do seu jeito)." C) "Tudo tem um propósito e um lugar certo." D) "Devagar se vai ao longe."
17. Em relação a regras e procedimentos: A) Gosto de flexibilidade, às vezes acho as regras limitantes e tento contorná-las. B) Uso as regras a meu favor para atingir objetivos, mas não hesito em quebrá-las se necessário e se eu puder controlar as consequências. C) Sigo as regras rigorosamente, acredito que elas garantem ordem e qualidade. D) Respeito as regras para evitar problemas, prefiro seguir o fluxo estabelecido.
18. Como você reage quando alguém está emocionalmente abalado? A) Tento animar a pessoa, conto piadas, ofereço distração e companhia. B) Ofereço soluções práticas para o problema, foco em resolver a situação que causou o abalo. C) Escuto com empatia, ofereço apoio profundo e tento compreender a dor da pessoa. D) Mantenho a calma, ofereço um ouvido atento e um ombro amigo, sem me deixar abalar muito.
19. Que tipo de filme ou livro você prefere? A) Comédias, aventuras, romances leves, algo que me divirta e me mantenha entretido. B) Ação, suspense, biografias de líderes, estratégias, algo que me desafie ou inspire poder. C) Dramas profundos, documentários, mistérios complexos, ficção científica filosófica, algo que me faça pensar e sentir. D) Histórias tranquilas, dramas familiares, romances amenos, natureza, algo que me relaxe e traga conforto.
20. O que é mais importante para você em um relacionamento (amizade, amoroso)? A) Diversão, cumplicidade, comunicação aberta e espontaneidade. B) Lealdade, objetivos em comum, apoio mútuo nas ambições. C) Compreensão profunda, fidelidade, apoio emocional e intelectual. D) Harmonia, estabilidade, aceitação mútua e tranquilidade.
21. Se você ganhasse na loteria, qual seria sua primeira reação/ação? A) Faria uma grande festa, viajaria pelo mundo, compraria presentes para todos! B) Investiria estrategicamente, planejaria como multiplicar o dinheiro, garantiria o controle financeiro. C) Pesquisaria as melhores opções de investimento, faria um plano detalhado de longo prazo, doaria para causas significativas. D) Guardaria a maior parte em segurança, faria algumas melhorias práticas na vida, evitaria mudanças drásticas.
22. Como você se sente em relação a riscos? A) Gosto de arriscar se a recompensa parecer divertida ou excitante, sou otimista. B) Calculo os riscos e assumo-os se acreditar que a recompensa vale a pena e que posso controlar a situação. C) Evito riscos desnecessários, prefiro a segurança e a previsibilidade, analiso tudo antes de agir. D) Desgosto de riscos, prefiro caminhos seguros e comprovados, a estabilidade é mais importante.
23. Sua memória tende a focar mais em: A) Momentos divertidos, pessoas interessantes, experiências marcantes (embora possa esquecer detalhes). B) Sucessos, fracassos (para aprender), injustiças cometidas contra você, quem te ajudou ou atrapalhou. C) Detalhes precisos, conversas significativas, erros cometidos (por você ou outros), sentimentos profundos. D) Fatos objetivos, rotinas, informações práticas, geralmente de forma neutra.
24. Quando aprende algo novo, você prefere: A) Experimentar na prática imediatamente, aprender fazendo, mesmo que cometa erros. B) Entender o objetivo e a aplicação prática rapidamente, focar no essencial para usar o conhecimento. C) Estudar a fundo a teoria, entender todos os porquês, buscar fontes confiáveis e dominar o assunto. D) Aprender em um ritmo calmo, com instruções claras e passo a passo, sem pressão.
25. Se descreva em uma palavra (escolha a que mais se aproxima): A) Entusiasmado(a) B) Determinado(a) C) Criterioso(a) D) Pacífico(a)
26. Como você lida com o silêncio em uma conversa? A) Sinto-me desconfortável e tento preenchê-lo rapidamente com qualquer assunto. B) Uso o silêncio estrategicamente ou o interrompo para direcionar a conversa. C) Posso apreciar o silêncio para refletir, ou me sentir um pouco ansioso dependendo do contexto. D) Sinto-me confortável com o silêncio, não sinto necessidade de preenchê-lo.
27. O que te deixa mais frustrado(a)? A) Tédio, falta de reconhecimento, ser ignorado. B) Incompetência alheia, falta de controle, obstáculos aos seus planos. C) Desorganização, falta de qualidade, injustiça, superficialidade. D) Conflitos interpessoais, pressão excessiva, desordem emocional.
28. Qual a sua relação com o passado, presente e futuro? A) Foco no presente e nas oportunidades imediatas, otimista em relação ao futuro, esqueço o passado facilmente. B) Foco no futuro (metas) e no presente (ações para alcançá-las), aprendo com o passado mas não me prendo a ele. C) Reflito muito sobre o passado (aprendizados, erros), analiso o presente e planejo o futuro com cautela, às vezes com preocupação. D) Vivo o presente de forma tranquila, valorizo a estabilidade e a continuidade do passado, vejo o futuro com serenidade.
29. Se você tivesse que organizar um evento, qual seria seu papel principal? A) Relações públicas, divulgação, animação, garantir que todos se divirtam. B) Coordenação geral, definição de metas, delegação de tarefas, garantir que tudo aconteça conforme o planejado (por você). C) Planejamento detalhado, logística, controle de qualidade, garantir que nada dê errado. D) Suporte, resolução de problemas de forma calma, garantir um ambiente harmonioso.
30. Qual ambiente de trabalho te agrada mais? A) Dinâmico, social, com muita interação, flexibilidade e novidades. B) Competitivo, desafiador, focado em resultados, onde eu possa liderar ou ter autonomia. C) Estruturado, quieto, onde eu possa me concentrar, com padrões claros de qualidade e tempo para análise. D) Estável, cooperativo, sem pressão, com relacionamentos harmoniosos e tarefas previsíveis.
Calculando seus Resultados:
Agora, conte quantas vezes você escolheu cada letra:
- Total de A: ______
- Total de B: ______
- Total de C: ______
- Total de D: ______
A letra (ou as letras) com a maior pontuação indica(m) seu(s) temperamento(s) dominante(s).
Interpretação dos Resultados:
-
Se sua maior pontuação foi A: Temperamento SANGUÍNEO Dominante
- Características: Você é extrovertido, otimista, sociável, comunicativo, entusiasmado e adora novidades. Gosta de ser o centro das atenções, faz amigos facilmente e contagia os outros com sua energia. É criativo e espontâneo.
- Pontos Fortes: Carismático, inspirador, adaptável, bom em iniciar relacionamentos e projetos, perdoa facilmente.
- Desafios Potenciais: Pode ser indisciplinado, desorganizado, impulsivo, superficial, ter dificuldade em focar e terminar tarefas, e ser muito dependente de aprovação externa.
-
Se sua maior pontuação foi B: Temperamento COLÉRICO Dominante
- Características: Você é enérgico, decidido, líder nato, orientado para metas e resultados. É ambicioso, assertivo, direto e não tem medo de desafios ou confrontos. Gosta de estar no controle e é muito prático.
- Pontos Fortes: Determinado, eficiente, líder natural, bom em tomar decisões e resolver problemas, autoconfiante.
- Desafios Potenciais: Pode ser impaciente, dominador, teimoso, insensível aos sentimentos alheios, propenso à raiva e a "atropelar" os outros para atingir seus objetivos.
-
Se sua maior pontuação foi C: Temperamento MELANCÓLICO Dominante
- Características: Você é introvertido, analítico, sensível, perfeccionista e profundo. É leal, dedicado, aprecia a beleza e a ordem. Tende a ser pensativo, criterioso e busca significado em tudo. Leva as coisas a sério.
- Pontos Fortes: Detalhista, organizado, criativo (em profundidade), leal, empático, comprometido com a qualidade e a justiça.
- Desafios Potenciais: Pode ser pessimista, excessivamente crítico (consigo e com os outros), indeciso (pela análise excessiva), guardar ressentimentos, ser propenso à tristeza e ao isolamento.
-
Se sua maior pontuação foi D: Temperamento FLEUMÁTICO Dominante
- Características: Você é calmo, tranquilo, equilibrado e diplomático. É observador, paciente, confiável e fácil de conviver. Evita conflitos, busca harmonia e estabilidade. É um bom ouvinte e trabalha bem sob rotina.
- Pontos Fortes: Pacífico, estável, confiável, bom ouvinte, diplomático, eficiente em tarefas rotineiras, mantém a calma sob pressão.
- Desafios Potenciais: Pode ser indeciso, procrastinador, resistente a mudanças, parecer apático ou sem entusiasmo, ter dificuldade em se impor e expressar suas próprias necessidades.
Combinações de Temperamentos:
É muito comum ter pontuações altas em duas letras. Isso indica uma combinação de temperamentos. Por exemplo:
- Sanguíneo-Colérico: Extrovertido, enérgico, líder carismático, mas pode ser impulsivo e dominador.
- Sanguíneo-Fleumático: Sociável e agradável, mas pode ter dificuldade com disciplina e iniciativa.
- Colérico-Melancólico: Líder focado e detalhista, muito capaz, mas pode ser excessivamente crítico e exigente.
- Melancólico-Fleumático: Quieto, confiável, analítico, mas pode ser indeciso e resistente a riscos.
Importante: Este teste é uma ferramenta de autoconhecimento. Ninguém se encaixa perfeitamente em uma única caixa. Use os resultados para entender melhor suas tendências naturais, seus pontos fortes e as áreas onde você pode buscar equilíbrio e desenvolvimento.
-
 @ e4950c93:1b99eccd
2025-05-16 10:14:50
@ e4950c93:1b99eccd
2025-05-16 10:14:50Joha est une marque danoise qui crée des vêtements en laine mérinos, coton biologique, viscose de bambou biologique et soie pour les bébés, les enfants et les femmes.
Matières naturelles utilisées dans les produits
- Coton (biologique)
- Laine (mérinos)
- Soie
- Cellulose régénérée (cupra, lyocell, modal, rayonne, viscose) (bambou biologique)
⚠️ Attention, certains produits de cette marque contiennent des matières non naturelles, dont : - Elasthanne, lycra, spandex - Polyamides, nylon
Catégories de produits proposés
Cette marque propose des produits intégralement en matière naturelle dans les catégories suivantes :
Vêtements
- Tailles vêtements: bébés, enfants, femmes
- Sous-vêtements: culottes
- Une pièce:
- Hauts: débardeurs, t-shirts
- Bas: pantalons, leggings
- Tête et mains: bonnets, cagoules, moufles
- Nuit: pyjamas
Chaussures
- Tailles chaussures: chaussures bébé
- Chaussons: botillons
Autres informations
- Certification Oeko-Tex Standard 100
- Certification Woolmark
- Déclaration de laine de mouton sans mulesing et de bien-être animal (Südwolle group GmbH)
👉 En savoir plus sur le site de la marque
Où trouver leurs produits ?
- Luna & Curious (en anglais, zone de livraison : RU et international)
- Niddle Noddle (en anglais, zone de livraison : RU et international)
- Chlidren Salon (en anglais, zone de livraison : RU et international)
- Lieblings Paris
Cet article est publié sur origine-nature.com 🌐 See this article in English
📝 Tu peux contribuer à cette fiche en suggérant une modification en commentaire.
🗣️ Tu utilises les produits de cette marque ? Partage ton avis en commentaire.
⚡ Heureu-x-se de trouver cette information ? Soutiens le projet en faisant un don, pour remercier les contribut-eur-ice-s.
-
 @ c4b5369a:b812dbd6
2025-04-15 07:26:16
@ c4b5369a:b812dbd6
2025-04-15 07:26:16Offline transactions with Cashu
Over the past few weeks, I've been busy implementing offline capabilities into nutstash. I think this is one of the key value propositions of ecash, beinga a bearer instrument that can be used without internet access.
 It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!
It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!What is ecash/Cashu?
Ecash is the first cryptocurrency ever invented. It was created by David Chaum in 1983. It uses a blind signature scheme, which allows users to prove ownership of a token without revealing a link to its origin. These tokens are what we call ecash. They are bearer instruments, meaning that anyone who possesses a copy of them, is considered the owner.
Cashu is an implementation of ecash, built to tightly interact with Bitcoin, more specifically the Bitcoin lightning network. In the Cashu ecosystem,
Mintsare the gateway to the lightning network. They provide the infrastructure to access the lightning network, pay invoices and receive payments. Instead of relying on a traditional ledger scheme like other custodians do, the mint issues ecash tokens, to represent the value held by the users.How do normal Cashu transactions work?
A Cashu transaction happens when the sender gives a copy of his ecash token to the receiver. This can happen by any means imaginable. You could send the token through email, messenger, or even by pidgeon. One of the common ways to transfer ecash is via QR code.
The transaction is however not finalized just yet! In order to make sure the sender cannot double-spend their copy of the token, the receiver must do what we call a
swap. A swap is essentially exchanging an ecash token for a new one at the mint, invalidating the old token in the process. This ensures that the sender can no longer use the same token to spend elsewhere, and the value has been transferred to the receiver.
What about offline transactions?
Sending offline
Sending offline is very simple. The ecash tokens are stored on your device. Thus, no internet connection is required to access them. You can litteraly just take them, and give them to someone. The most convenient way is usually through a local transmission protocol, like NFC, QR code, Bluetooth, etc.
The one thing to consider when sending offline is that ecash tokens come in form of "coins" or "notes". The technical term we use in Cashu is
Proof. It "proofs" to the mint that you own a certain amount of value. Since these proofs have a fixed value attached to them, much like UTXOs in Bitcoin do, you would need proofs with a value that matches what you want to send. You can mix and match multiple proofs together to create a token that matches the amount you want to send. But, if you don't have proofs that match the amount, you would need to go online and swap for the needed proofs at the mint.Another limitation is, that you cannot create custom proofs offline. For example, if you would want to lock the ecash to a certain pubkey, or add a timelock to the proof, you would need to go online and create a new custom proof at the mint.
Receiving offline
You might think: well, if I trust the sender, I don't need to be swapping the token right away!
You're absolutely correct. If you trust the sender, you can simply accept their ecash token without needing to swap it immediately.
This is already really useful, since it gives you a way to receive a payment from a friend or close aquaintance without having to worry about connectivity. It's almost just like physical cash!
It does however not work if the sender is untrusted. We have to use a different scheme to be able to receive payments from someone we don't trust.
Receiving offline from an untrusted sender
To be able to receive payments from an untrusted sender, we need the sender to create a custom proof for us. As we've seen before, this requires the sender to go online.
The sender needs to create a token that has the following properties, so that the receciver can verify it offline:
- It must be locked to ONLY the receiver's public key
- It must include an
offline signature proof(DLEQ proof) - If it contains a timelock & refund clause, it must be set to a time in the future that is acceptable for the receiver
- It cannot contain duplicate proofs (double-spend)
- It cannot contain proofs that the receiver has already received before (double-spend)

If all of these conditions are met, then the receiver can verify the proof offline and accept the payment. This allows us to receive payments from anyone, even if we don't trust them.
At first glance, this scheme seems kinda useless. It requires the sender to go online, which defeats the purpose of having an offline payment system.
I beleive there are a couple of ways this scheme might be useful nonetheless:
-
Offline vending machines: Imagine you have an offline vending machine that accepts payments from anyone. The vending machine could use this scheme to verify payments without needing to go online itself. We can assume that the sender is able to go online and create a valid token, but the receiver doesn't need to be online to verify it.
-
Offline marketplaces: Imagine you have an offline marketplace where buyers and sellers can trade goods and services. Before going to the marketplace the sender already knows where he will be spending the money. The sender could create a valid token before going to the marketplace, using the merchants public key as a lock, and adding a refund clause to redeem any unspent ecash after it expires. In this case, neither the sender nor the receiver needs to go online to complete the transaction.
How to use this
Pretty much all cashu wallets allow you to send tokens offline. This is because all that the wallet needs to do is to look if it can create the desired amount from the proofs stored locally. If yes, it will automatically create the token offline.
Receiving offline tokens is currently only supported by nutstash (experimental).
To create an offline receivable token, the sender needs to lock it to the receiver's public key. Currently there is no refund clause! So be careful that you don't get accidentally locked out of your funds!

The receiver can then inspect the token and decide if it is safe to accept without a swap. If all checks are green, they can accept the token offline without trusting the sender.

The receiver will see the unswapped tokens on the wallet homescreen. They will need to manually swap them later when they are online again.
 Later when the receiver is online again, they can swap the token for a fresh one.
Later when the receiver is online again, they can swap the token for a fresh one.
Summary
We learned that offline transactions are possible with ecash, but there are some limitations. It either requires trusting the sender, or relying on either the sender or receiver to be online to verify the tokens, or create tokens that can be verified offline by the receiver.
I hope this short article was helpful in understanding how ecash works and its potential for offline transactions.
Cheers,
Gandlaf
-
 @ 266815e0:6cd408a5
2025-04-15 06:58:14
@ 266815e0:6cd408a5
2025-04-15 06:58:14Its been a little over a year since NIP-90 was written and merged into the nips repo and its been a communication mess.
Every DVM implementation expects the inputs in slightly different formats, returns the results in mostly the same format and there are very few DVM actually running.
NIP-90 is overloaded
Why does a request for text translation and creating bitcoin OP_RETURNs share the same input
itag? and why is there anoutputtag on requests when only one of them will return an output?Each DVM request kind is for requesting completely different types of compute with diffrent input and output requirements, but they are all using the same spec that has 4 different types of inputs (
text,url,event,job) and an undefined number ofoutputtypes.Let me show a few random DVM requests and responses I found on
wss://relay.damus.ioto demonstrate what I mean:This is a request to translate an event to English
json { "kind": 5002, "content": "", "tags": [ // NIP-90 says there can be multiple inputs, so how would a DVM handle translatting multiple events at once? [ "i", "<event-id>", "event" ], [ "param", "language", "en" ], // What other type of output would text translations be? image/jpeg? [ "output", "text/plain" ], // Do we really need to define relays? cant the DVM respond on the relays it saw the request on? [ "relays", "wss://relay.unknown.cloud/", "wss://nos.lol/" ] ] }This is a request to generate text using an LLM model
json { "kind": 5050, // Why is the content empty? wouldn't it be better to have the prompt in the content? "content": "", "tags": [ // Why use an indexable tag? are we ever going to lookup prompts? // Also the type "prompt" isn't in NIP-90, this should probably be "text" [ "i", "What is the capital of France?", "prompt" ], [ "p", "c4878054cff877f694f5abecf18c7450f4b6fdf59e3e9cb3e6505a93c4577db2" ], [ "relays", "wss://relay.primal.net" ] ] }This is a request for content recommendation
json { "kind": 5300, "content": "", "tags": [ // Its fine ignoring this param, but what if the client actually needs exactly 200 "results" [ "param", "max_results", "200" ], // The spec never mentions requesting content for other users. // If a DVM didn't understand this and responded to this request it would provide bad data [ "param", "user", "b22b06b051fd5232966a9344a634d956c3dc33a7f5ecdcad9ed11ddc4120a7f2" ], [ "relays", "wss://relay.primal.net", ], [ "p", "ceb7e7d688e8a704794d5662acb6f18c2455df7481833dd6c384b65252455a95" ] ] }This is a request to create a OP_RETURN message on bitcoin
json { "kind": 5901, // Again why is the content empty when we are sending human readable text? "content": "", "tags": [ // and again, using an indexable tag on an input that will never need to be looked up ["i", "09/01/24 SEC Chairman on the brink of second ETF approval", "text"] ] }My point isn't that these event schema's aren't understandable but why are they using the same schema? each use-case is different but are they all required to use the same
itag format as input and could support all 4 types of inputs.Lack of libraries
With all these different types of inputs, params, and outputs its verify difficult if not impossible to build libraries for DVMs
If a simple text translation request can have an
eventortextas inputs, apayment-requiredstatus at any point in the flow, partial results, or responses from 10+ DVMs whats the best way to build a translation library for other nostr clients to use?And how do I build a DVM framework for the server side that can handle multiple inputs of all four types (
url,text,event,job) and clients are sending all the requests in slightly differently.Supporting payments is impossible
The way NIP-90 is written there isn't much details about payments. only a
payment-requiredstatus and a genericamounttagBut the way things are now every DVM is implementing payments differently. some send a bolt11 invoice, some expect the client to NIP-57 zap the request event (or maybe the status event), and some even ask for a subscription. and we haven't even started implementing NIP-61 nut zaps or cashu A few are even formatting the
amountnumber wrong or denominating it in sats and not mili-satsBuilding a client or a library that can understand and handle all of these payment methods is very difficult. for the DVM server side its worse. A DVM server presumably needs to support all 4+ types of payments if they want to get the most sats for their services and support the most clients.
All of this is made even more complicated by the fact that a DVM can ask for payment at any point during the job process. this makes sense for some types of compute, but for others like translations or user recommendation / search it just makes things even more complicated.
For example, If a client wanted to implement a timeline page that showed the notes of all the pubkeys on a recommended list. what would they do when the selected DVM asks for payment at the start of the job? or at the end? or worse, only provides half the pubkeys and asks for payment for the other half. building a UI that could handle even just two of these possibilities is complicated.
NIP-89 is being abused
NIP-89 is "Recommended Application Handlers" and the way its describe in the nips repo is
a way to discover applications that can handle unknown event-kinds
Not "a way to discover everything"
If I wanted to build an application discovery app to show all the apps that your contacts use and let you discover new apps then it would have to filter out ALL the DVM advertisement events. and that's not just for making requests from relays
If the app shows the user their list of "recommended applications" then it either has to understand that everything in the 5xxx kind range is a DVM and to show that is its own category or show a bunch of unknown "favorites" in the list which might be confusing for the user.
In conclusion
My point in writing this article isn't that the DVMs implementations so far don't work, but that they will never work well because the spec is too broad. even with only a few DVMs running we have already lost interoperability.
I don't want to be completely negative though because some things have worked. the "DVM feeds" work, although they are limited to a single page of results. text / event translations also work well and kind
5970Event PoW delegation could be cool. but if we want interoperability, we are going to need to change a few things with NIP-90I don't think we can (or should) abandon NIP-90 entirely but it would be good to break it up into small NIPs or specs. break each "kind" of DVM request out into its own spec with its own definitions for expected inputs, outputs and flow.
Then if we have simple, clean definitions for each kind of compute we want to distribute. we might actually see markets and services being built and used.
-
 @ eb0157af:77ab6c55
2025-05-16 10:09:27
@ eb0157af:77ab6c55
2025-05-16 10:09:27The sovereign fund Mubadala increases its holdings in BlackRock’s Bitcoin ETF by 6%.
According to the 13-F filing submitted to the SEC, Abu Dhabi’s sovereign wealth fund Mubadala has increased its holdings in BlackRock’s spot Bitcoin ETF (IBIT) to 8.73 million shares, with a total value of $408.5 million.

Source: Sec
The investment marks a 6% increase compared to its position last December, when the fund held 8.23 million shares.
For several months now, some of the world’s largest sovereign wealth funds have already gained exposure to Bitcoin: Norway’s Government Pension Fund Global, the largest in the world, holds around $500 million in MicroStrategy shares, while Abu Dhabi’s ADQ regularly invests in digital asset-related projects.
Mubadala joins other major institutional investors, including Goldman Sachs and Avenir Group, in increasing their exposure to IBIT.
The post Abu Dhabi sovereign wealth fund invests $408.5 million in Bitcoin via IBIT appeared first on Atlas21.
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ eb0157af:77ab6c55
2025-05-16 08:52:31
@ eb0157af:77ab6c55
2025-05-16 08:52:31The ECB claims that a digital euro is essential to preserve the role of cash in the growing digital economy.
The European Central Bank (ECB) is moving forward with plans for a digital euro, considering it crucial for maintaining European monetary sovereignty in the digital era.
On May 15, Piero Cipollone, member of the ECB Executive Board, highlighted during the France Payments Forum how the use of physical cash is rapidly declining. With the surge in digital transactions and e-commerce, the ECB believes a digital euro represents a crucial step to preserve the universal function of cash in a digitized form.
The dependencies of Europe’s payment sector
According to the Eurotower, the current European payment system has several vulnerabilities. About two-thirds of card transactions in the eurozone are processed by non-European companies, and as many as 13 euro area countries rely entirely on international payment networks for point-of-sale transactions.
Even countries with national card systems must collaborate with international networks to enable cross-border or online purchases. Players like PayPal, Apple Pay, and Alipay dominate digital payment solutions, often partnering with international networks to further expand their market presence.
The digital euro as a complement to cash
The ECB has stressed that the digital euro will not replace cash but will serve alongside it as legal tender, ensuring it is accepted wherever digital payments are available. One key feature, according to the central institution, will be offline functionality — offering users privacy similar to that of cash payments and enabling transactions even without network connectivity.
Beyond retail payments, the ECB is also advancing in the implementation of distributed ledger technologies (DLT) and tokenization to facilitate wholesale financial transactions. The ECB has announced it will soon provide tools to settle DLT-based transactions using central bank money.
The post Digital euro to restore cash’s role, says ECB appeared first on Atlas21.
-
 @ 9223d2fa:b57e3de7
2025-04-15 02:54:00
@ 9223d2fa:b57e3de7
2025-04-15 02:54:0012,600 steps
-
 @ 6e0ea5d6:0327f353
2025-04-14 15:11:17
@ 6e0ea5d6:0327f353
2025-04-14 15:11:17Ascolta.
We live in times where the average man is measured by the speeches he gives — not by the commitments he keeps. People talk about dreams, goals, promises… but what truly remains is what’s honored in the silence of small gestures, in actions that don’t seek applause, in attitudes unseen — yet speak volumes.
Punctuality, for example. Showing up on time isn’t about the clock. It’s about respect. Respect for another’s time, yes — but more importantly, respect for one’s own word. A man who is late without reason is already running late in his values. And the one who excuses his own lateness with sweet justifications slowly gets used to mediocrity.
Keeping your word is more than fulfilling promises. It is sealing, with the mouth, what the body must later uphold. Every time a man commits to something, he creates a moral debt with his own dignity. And to break that commitment is to declare bankruptcy — not in the eyes of others, but in front of himself.
And debts? Even the small ones — or especially the small ones — are precise thermometers of character. A forgotten sum, an unpaid favor, a commitment left behind… all of these reveal the structure of the inner building that man resides in. He who neglects the small is merely rehearsing for his future collapse.
Life, contrary to what the reckless say, is not built on grand deeds. It is built with small bricks, laid with almost obsessive precision. The truly great man is the one who respects the details — recognizing in them a code of conduct.
In Sicily, especially in the streets of Palermo, I learned early on that there is more nobility in paying a five-euro debt on time than in flaunting riches gained without word, without honor, without dignity.
As they say in Palermo: L’uomo si conosce dalle piccole cose.
So, amico mio, Don’t talk to me about greatness if you can’t show up on time. Don’t talk to me about respect if your word is fickle. And above all, don’t talk to me about honor if you still owe what you once promised — no matter how small.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ b423e216:3280b1c0
2025-05-16 08:27:58
@ b423e216:3280b1c0
2025-05-16 08:27:58Im digitalen Zeitalter wird der Schutz der Privatsphäre immer wichtiger. Unabhängig davon, ob es sich um eine Regierungsbehörde, ein Unternehmen oder eine Einzelperson handelt, besteht für alle das Risiko, abgehört oder verfolgt zu werden. Mobiltelefone, WLAN, GPS und UHF-Geräte (Ultrahochfrequenz) können zu Werkzeugen für Hacker oder Überwachungsgeräte werden. Um diesen Bedrohungen entgegenzuwirken, sind Signalstörsender (wie etwa Tragbare Handyblocker, WLAN-Störsender, GPS-Störsender und UHF-Störsender) zu einem wirksamen Mittel zum Schutz der Privatsphäre geworden. In diesem Artikel werden die verschiedenen Arten von Störsendern erläutert, wie sie funktionieren und wie man sie legal und angemessen einsetzt, um Abhören und Tracking zu verhindern.
1. Was ist ein Signalstörsender?
Ein Signalstörsender ist ein elektronisches Gerät, das die Kommunikationssignale eines Zielgeräts durch die Aussendung von Radiowellen einer bestimmten Frequenz stört oder blockiert. Es kann Mobiltelefonanrufe, WLAN-Verbindungen, GPS-Positionierung oder UHF-Signalübertragungen blockieren, um Abhören oder Tracking zu verhindern.
Das Funktionsprinzip eines Störsenders besteht darin, ein Rauschsignal mit hoher Intensität an das Zielfrequenzband zu senden, wodurch es für das empfangende Gerät unmöglich wird, das ursprüngliche Signal richtig zu interpretieren. Beispielsweise blockiert ein Handy-Störsender die Kommunikation zwischen einem Handy und einer Basisstation, sodass mit dem Handy weder Anrufe getätigt noch Textnachrichten empfangen werden können.
2. Gängige Arten von Signalstörern
(1) Handy-Störsender
Tragbare störsender für handy werden hauptsächlich verwendet, um GSM-, 3G UMTS-, 4G- und 5G-Signale zu blockieren. Es kann verhindern, dass das Telefon überwacht oder geortet wird und eignet sich für die folgenden Szenarien:
- Abhören verhindern: Verhindern Sie, dass das Mikrofon Ihres Telefons während wichtiger Besprechungen oder privater Gespräche aus der Ferne aktiviert wird.
- Anti-Tracking: Blockieren Sie die GPS- und Mobilfunknetzortung, um die Verfolgung durch Malware oder Hacker zu verhindern.
- Prävention von Prüfungsbetrug: Wird in Schulen oder Prüfungssälen verwendet, um zu verhindern, dass Kandidaten mit Mobiltelefonen schummeln.
(2) WLAN-Störsender
WLAN-Störsender können drahtlose Netzwerksignale in den Frequenzbändern 2,4 GHz und 5 GHz blockieren und eignen sich für:
- Hacking verhindern: Blockieren Sie WLAN-Signale in der Nähe, um Datendiebstahl zu verhindern.
- Smart-Home-Geräte schützen: Verhindern Sie die Fernsteuerung von Smart-Kameras, Lautsprechern und anderen Geräten.
- Militärische oder staatliche vertrauliche Bereiche: Verhindern Sie, dass durch drahtlose Signale vertrauliche Informationen preisgegeben werden.
(3) GPS-Störsender
GPS-Störsender können Satellitenpositionierungssignale blockieren, um die Verfolgung von Fahrzeugen oder Mobiltelefonen zu verhindern. Sie eignen sich für:
- Schützen Sie Ihre Privatsphäre: Verhindern Sie, dass Mitfahrdienste, Essenslieferdienste oder Malware Ihren Aufenthaltsort aufzeichnen.
- Militärische Nutzung: Verhindern, dass Drohnen oder Raketen für ihren Angriff auf GPS-Navigation angewiesen sind.
- Anti-Aufklärung: Verhindern Sie Wirtschaftsspionage oder die Verfolgung von Logistikfahrzeugen durch Wettbewerber.
(4) UHF-Störsender
UHF Jammer (Ultra High Frequency) werden hauptsächlich verwendet, um drahtlose Kommunikation im Frequenzband von 300 MHz bis 3 GHz zu blockieren, wie z. B. Walkie-Talkies, drahtlose Mikrofone, RFID usw. und eignen sich für:
- Verhindern Sie drahtloses Abhören: Blockieren Sie drahtlose Abhörgeräte, die von Spionen verwendet werden.
- RFID-Daten schützen: Verhindern Sie das illegale Scannen von Kreditkarten oder Zugangskarten.
- Anti-Drohnen-Störsender: Blockiert die Fernbedienungssignale von Drohnen, um zu verhindern, dass sie sich sensiblen Bereichen nähern.
3. Wie verwendet man Signalstörsender richtig, um die Privatsphäre zu schützen?
Obwohl Störsender das Abhören und Verfolgen wirksam verhindern können, kann eine unsachgemäße Verwendung gegen das Gesetz verstoßen oder die normale Kommunikation beeinträchtigen. Hier sind einige Vorschläge für den legalen und sinnvollen Einsatz von Störsendern:
(1) Verstehen Sie die örtlichen Gesetze
- In vielen Ländern ist die unbefugte Verwendung von Störsendern illegal und kann zu Geldstrafen oder strafrechtlichen Konsequenzen führen.
- Nur zur Verwendung im privaten Bereich oder dort, wo dies gesetzlich zulässig ist, z. B. beim Militär, in der Regierung oder bei der Unternehmenssicherheit.
(2) Wählen Sie den entsprechenden Störbereich
- WLAN Signal Blocker mit geringer Leistung eignen sich für kleine Besprechungsräume oder Fahrzeuge, um die Kommunikation in der Umgebung nicht zu beeinträchtigen.
- In großen Veranstaltungsorten können Störsender mit hoher Leistung eingesetzt werden, dabei ist jedoch Vorsicht geboten, um die öffentliche Kommunikation nicht zu stören.
(3) Kombiniert mit anderen Sicherheitsmaßnahmen
- Störsender sind nur eine vorübergehende Lösung. Für einen langfristigen Schutz der Privatsphäre ist die Verwendung verschlüsselter Kommunikation, VPNs, Abhörgeräte usw. erforderlich.
(4) Regelmäßige Überprüfung der Ausrüstung
- Störsender können aufgrund von Änderungen der Signalstärke unwirksam werden und müssen regelmäßig getestet und angepasst werden.
4. Einschränkungen von Störsendern
Obwohl Störsender Signale wirksam blockieren können, unterliegen sie dennoch einigen Einschränkungen:
- Verhindert kein kabelgebundenes Abhören: Störsender wirken nur gegen drahtlose Signale und schützen nicht vor physischen Abhörgeräten (wie versteckten Mikrofonen).
- Kann legitime Kommunikation beeinträchtigen: Störsender blockieren wahllos Signale, was Notrufe oder die normale WLAN-Nutzung beeinträchtigen kann.
- Kann durch Anti-Jamming-Technologie geknackt werden: Einige fortschrittliche Geräte verwenden möglicherweise Frequenzsprungtechnologie (z. B. militärische Kommunikation), die von gewöhnlichen Störsendern nur schwer vollständig blockiert werden kann.
5. Alternativen: Sicherere Methoden zum Schutz der Privatsphäre
Wenn der Einsatz von Auto GPS Tracker Störsender eingeschränkt ist, ziehen Sie die folgenden Alternativen in Betracht:
- Verwenden Sie einen Faradayschen Käfig: Eine metallische Abschirmhülle oder ein Raum, der drahtlose Signale vollständig blockiert.
- Flugmodus aktivieren: Durch das Ausschalten der drahtlosen Mobiltelefonkommunikation wird die Fernaktivierung des Mikrofons verhindert.
- Verwenden Sie verschlüsselte Kommunikationstools: z. B. Anwendungen mit End-to-End-Verschlüsselung wie Signal, ProtonMail usw.
abschließend
Ein Signalstörsender ist ein leistungsstarkes Tool zum Schutz der Privatsphäre, das das Abhören von Mobiltelefonen, WLAN-Hacking, GPS-Tracking und UHF-Überwachung wirksam verhindern kann. Allerdings ist die Verwendung gesetzlich eingeschränkt und sollte mit Vorsicht verwendet werden. Durch die Kombination von Störsendern mit anderen Sicherheitsmaßnahmen (wie verschlüsselter Kommunikation und physischer Abschirmung) kann die Privatsphäre im Rahmen des gesetzlich Gegebenen weitestgehend vor Verletzungen geschützt werden. Mit der Entwicklung von Technologien zum Abhören von Störsendern könnten diese in Zukunft intelligenter und präziser werden und sich zu einem wichtigen Mittel zum Schutz der Privatsphäre entwickeln.
- https://www.signaljammerphone.com/de/echte-gefahren-durch-versteckte-kameras-und-ein-leitfaden-zur-abwehr.html
- https://www.signaljammerphone.com/de/J-DR6-leistungsstarker-tragbare-rucksack-drohnen-fernsteuerungs-stoerer-300W.html
- https://www.signaljammerphone.com/de/wie-kann-man-funkwellen-wirksam-blockieren-funkwellenabschirmung-und-stoertechnologie.html
-
 @ f4db5270:3c74e0d0
2025-05-16 08:13:05
@ f4db5270:3c74e0d0
2025-05-16 08:13:05Hi Art lover! 🎨🫂💜
You may not know it yet but all of the following paintings are available in #Bitcoin on my website: <https://isolabellart.carrd.co/>
For info and prices write to me in DM and we will find a good deal! 🤝
 THE QUIET ROOM 50x40cm, Oil on board - Completed May 8, 2025
THE QUIET ROOM 50x40cm, Oil on board - Completed May 8, 2025
 OLTRE LA NEBBIA 50x40cm, Oil on board - Completed April 18, 2025
OLTRE LA NEBBIA 50x40cm, Oil on board - Completed April 18, 2025
 TO THE LAST LIGHT 50x40cm, Oil on board - Completed April 5, 2025
TO THE LAST LIGHT 50x40cm, Oil on board - Completed April 5, 2025
 BLINDING SUNSET 40x40cm, Oil on board - Completed March 18, 2025
BLINDING SUNSET 40x40cm, Oil on board - Completed March 18, 2025
 ECHI DEL TEMPO PERDUTO 40x40cm, Oil on board - Completed March 09, 2025
ECHI DEL TEMPO PERDUTO 40x40cm, Oil on board - Completed March 09, 2025
 EVANESCENZE 40x40cm, Oil on board - Completed February 11, 2025
EVANESCENZE 40x40cm, Oil on board - Completed February 11, 2025
 OLTRE LA STACCIONATA 50x40cm, Oil on board - Completed February 8, 2025
OLTRE LA STACCIONATA 50x40cm, Oil on board - Completed February 8, 2025
 LONELY WINDMILL 50x40cm, Oil on board - Completed January 30, 2025
LONELY WINDMILL 50x40cm, Oil on board - Completed January 30, 2025
 ON THE ROAD AGAIN 40x50cm, Oil on canvas - Completed January 23, 2025
ON THE ROAD AGAIN 40x50cm, Oil on canvas - Completed January 23, 2025
 SUN OF JANUARY 40x50cm, Oil on canvas - Completed January 14, 2025
SUN OF JANUARY 40x50cm, Oil on canvas - Completed January 14, 2025

THE BLUE HOUR 40x50cm, Oil on canvas - Completed December 14, 2024
 WHERE WINTER WHISPERS 50x40cm, Oil on canvas - Completed November 07, 2024
WHERE WINTER WHISPERS 50x40cm, Oil on canvas - Completed November 07, 2024
 L'ATTESA DI UN MOMENTO 40x40cm, Oil on canvas - Completed October 29, 2024
L'ATTESA DI UN MOMENTO 40x40cm, Oil on canvas - Completed October 29, 2024

LE COSE CHE PENSANO 40x50cm, Oil on paper - Completed October 05, 2024
 TWILIGHT'S RIVER 50x40cm, Oil on canvas - Completed September 17, 2024
TWILIGHT'S RIVER 50x40cm, Oil on canvas - Completed September 17, 2024

GOLD ON THE OCEAN 40x50cm, Oil on paper - Completed September 08, 2024
 SUSSURRI DI CIELO E MARE 50x40cm, Oil on paper - Completed September 05, 2024
SUSSURRI DI CIELO E MARE 50x40cm, Oil on paper - Completed September 05, 2024
 THE END OF A WONDERFUL WEEKEND 40x30cm, Oil on board - Completed August 12, 2024
THE END OF A WONDERFUL WEEKEND 40x30cm, Oil on board - Completed August 12, 2024
 FIAMME NEL CIELO 60x35cm, Oil on board - Completed July 28, 2024
FIAMME NEL CIELO 60x35cm, Oil on board - Completed July 28, 2024
 INIZIO D'ESTATE 50x40cm, Oil on cradled wood panel Completed July 13, 2024
INIZIO D'ESTATE 50x40cm, Oil on cradled wood panel Completed July 13, 2024
 OMBRE DELLA SERA 50x40cm, Oil on cradled wood panel - Completed June 16, 2024
OMBRE DELLA SERA 50x40cm, Oil on cradled wood panel - Completed June 16, 2024
 NEW ZEALAND SUNSET 80x60cm, Oil on canvas board - Completed May 28, 2024
NEW ZEALAND SUNSET 80x60cm, Oil on canvas board - Completed May 28, 2024
 VENICE 50x40cm, Oil on board - Completed May 4, 2024
VENICE 50x40cm, Oil on board - Completed May 4, 2024
 CORNWALL 50x40cm, Oil on board - Completed April 26, 2024
CORNWALL 50x40cm, Oil on board - Completed April 26, 2024
 DOCKS ON SUNSET 40x19,5cm, Oil on board Completed March 14, 2024
DOCKS ON SUNSET 40x19,5cm, Oil on board Completed March 14, 2024
 SOLITUDE 30x30cm, Oil on cradled wood panel - Completed March 2, 2024
SOLITUDE 30x30cm, Oil on cradled wood panel - Completed March 2, 2024
 LULLING WAVES 40x30cm, Oil on cradled wood panel - Completed January 14, 2024
LULLING WAVES 40x30cm, Oil on cradled wood panel - Completed January 14, 2024
 MULATTIERA IN AUTUNNO 30x30cm, Oil on cradled wood panel - Completed November 23, 2023
MULATTIERA IN AUTUNNO 30x30cm, Oil on cradled wood panel - Completed November 23, 2023
 TRAMONTO A KOS 40x40cm, oil on board canvas - Completed November 7, 2023
TRAMONTO A KOS 40x40cm, oil on board canvas - Completed November 7, 2023
 HIDDEN SMILE 40x40cm, oil on board - Completed September 28, 2023
HIDDEN SMILE 40x40cm, oil on board - Completed September 28, 2023
 INIZIO D'AUTUNNO 40x40cm, oil on canvas - Completed September 23, 2023
INIZIO D'AUTUNNO 40x40cm, oil on canvas - Completed September 23, 2023
 BOE NEL LAGO 30x30cm, oil on canvas board - Completed August 15, 2023
BOE NEL LAGO 30x30cm, oil on canvas board - Completed August 15, 2023
 BARCHE A RIPOSO 40x40cm, oil on canvas board - Completed July 25, 2023
BARCHE A RIPOSO 40x40cm, oil on canvas board - Completed July 25, 2023

IL RISVEGLIO 30x40cm, oil on canvas board - Completed July 18, 2023

LA QUIETE PRIMA DELLA TEMPESTA 30x40cm, oil on canvas board - Completed March 30, 2023
 LAMPIONE SUL LAGO 30x30cm, oil on canvas board - Completed March 05, 2023
LAMPIONE SUL LAGO 30x30cm, oil on canvas board - Completed March 05, 2023
 DUE NELLA NEVE 60x25cm, oil on board - Completed February 4, 2023
DUE NELLA NEVE 60x25cm, oil on board - Completed February 4, 2023
 UNA CAREZZA 30x30cm, oil on canvas board - Completed January 17, 2023
UNA CAREZZA 30x30cm, oil on canvas board - Completed January 17, 2023
 REBEL WAVES 44x32cm, oil on canvas board
REBEL WAVES 44x32cm, oil on canvas board
 THE SCREAMING WAVE 40x30cm, oil on canvas board
THE SCREAMING WAVE 40x30cm, oil on canvas board

"LA DONZELLETTA VIEN DALLA CAMPAGNA..." 30x40cm, oil on canvas board

LIGHTHOUSE ON WHITE CLIFF 30x40cm, oil on canvas board
-
 @ 6e0ea5d6:0327f353
2025-04-14 15:10:58
@ 6e0ea5d6:0327f353
2025-04-14 15:10:58Ascolta bene.
A man’s collapse never begins on the battlefield.
It begins in the invisible antechamber of his own mind.
Before any public fall, there is an ignored internal whisper—
a small, quiet, private decision that gradually drags him toward ruin.No empire ever fell without first rotting from within.
The world does not destroy a man who hasn’t first surrendered to himself.
The enemy outside only wins when it finds space in the void the man has silently carved.**Non ti sbagliare ** — there are no armies more ruthless than undisciplined thoughts.
There are no blows more fatal than the ones we deal ourselves:
with small concessions, well-crafted excuses,
and the slow deterioration of our integrity.
What people call failure is nothing more than the logical outcome
of a sequence of internal betrayals.Afraid of the world? Sciocchezze.
But a man who’s already bowed before his own weaknesses—
he needs no enemies.
He digs his own grave, chooses the epitaph,
and the only thing the world does is toss in some dirt.Capisci?
Strength isn’t the absence of falling, but the presence of resistance.
The true battle isn’t external.
It takes place within—where there’s only you, your conscience, and the mirror.
And it’s in that silent courtroom where everything is decided.The discipline to say “no” to yourself
is more noble than any public glory.
Self-control is more valuable than any victory over others.In Sicily, we learn early:
“Cu s’abbrazza cu’ so’ nemicu, si scorda la faccia di l’amicu.”
He who embraces his enemy forgets the face of his friend.
The most dangerous enemy is the one you feed daily with self-indulgence.
And the most relentless confrontation is the one you avoid in front of the mirror.So don’t talk to me about external defeats.
Tell me where inside you the weakness began.
Tell me the exact moment you abandoned what you believed in, in the name of ease.
Because a man only falls before the world… after falling before himself.Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ c21b1a6c:0cd4d170
2025-04-14 14:41:20
@ c21b1a6c:0cd4d170
2025-04-14 14:41:20🧾 Progress Report Two
Hey everyone! I’m back with another progress report for Formstr, a part of the now completed grant from nostr:npub10pensatlcfwktnvjjw2dtem38n6rvw8g6fv73h84cuacxn4c28eqyfn34f . This update covers everything we’ve built since the last milestone — including polish, performance, power features, and plenty of bug-squashing.
🏗️ What’s New Since Last Time?
This quarter was less about foundational rewrites and more about production hardening and real-world feedback. With users now onboard, our focus shifted to polishing UX, fixing issues, and adding new features that made Formstr easier and more powerful to use.
✨ New Features & UX Improvements
- Edit Existing Forms
- Form Templates
- Drag & Drop Enhancements (especially for mobile)
- New Public Forms UX (card-style layout)
- FAQ & Support Sections
- Relay Modal for Publishing
- Skeleton Loaders and subtle UI Polish
🐛 Major Bug Fixes
- Fixed broken CSV exports when responses were empty
- Cleaned up mobile rendering issues for public forms
- Resolved blank.ts export issues and global form bugs
- Fixed invalid
npubstrings in the admin flow - Patched response handling for private forms
- Lots of small fixes for titles, drafts, embedded form URLs, etc.
🔐 Access Control & Privacy
- Made forms private by default
- Fixed multiple issues around form visibility, access control UIs, and anonymous submissions
- Improved detection of pubkey issues in shared forms
🚧 Some Notable In-Progress Features
The following features are actively being developed, and many are nearing completion:
-
Conditional Questions:
This one’s been tough to crack, but we’re close!
Work in progress bykeralissand myself:
👉 PR #252 -
Downloadable Forms:
Fully-contained downloadable HTML versions of forms.
Being led bycasyazmonwith initial code by Basanta Goswami
👉 PR #274 -
OLLAMA Integration (Self-Hosted LLMs):
Users will be able to create forms using locally hosted LLMs.
PR byashu01304
👉 PR #247 -
Sections in Forms:
Work just started on adding section support!
Small PoC PR bykeraliss:
👉 PR #217
🙌 Huge Thanks to New Contributors
We've had amazing contributors this cycle. Big thanks to:
- Aashutosh Gandhi (ashu01304) – drag-and-drop enhancements, OLLAMA integration
- Amaresh Prasad (devAmaresh) – fixed npub and access bugs
- Biresh Biswas (Billa05) – skeleton loaders
- Shashank Shekhar Singh (Shashankss1205) – bugfixes, co-authored image patches
- Akap Azmon Deh-nji (casyazmon) – CSV fixes, downloadable forms
- Manas Ranjan Dash (mdash3735) – bug fixes
- Basanta Goswami – initial groundwork for downloadable forms
- keraliss – ongoing work on conditional questions and sections
We also registered for the Summer of Bitcoin program and have been receiving contributions from some incredibly bright new applicants.
🔍 What’s Still Coming?
From the wishlist I committed to during the grant, here’s what’s still in the oven:
-[x] Upgrade to nip-44 - [x] Access Controlled Forms: A Form will be able to have multiple admins and Editors. - [x] Private Forms and Fixed Participants: Enncrypt a form and only allow certain npubs to fill it. - [x] Edit Past Forms: Being able to edit an existing form. - [x] Edit Past Forms
- [ ] Conditional Rendering (in progress)
- [ ] Sections (just started)
- [ ] Integrations - OLLAMA / AI-based Form Generation (near complete)
- [ ] Paid Surveys
- [ ] NIP-42 Private Relay support
❌ What’s De-Prioritized?
- Nothing is de-prioritized now especially since Ollama Integration got re-prioritized (thanks to Summer Of Bitcoin). We are a little delayed on Private Relays support but it's now becoming a priority and in active development. Zap Surveys will be coming soon too.
💸 How Funds Were Used
- Paid individual contributors for their work.
- Living expenses to allow full-time focus on development
🧠 Closing Thoughts
Things feel like they’re coming together now. We’re out of "beta hell", starting to see real adoption, and most importantly, gathering feedback from real users. That’s helping us make smarter choices and move fast without breaking too much.
Stay tuned for the next big drop — and in the meantime, try creating a form at formstr.app, and let me know what you think!
-
 @ 57d1a264:69f1fee1
2025-05-16 07:51:08
@ 57d1a264:69f1fee1
2025-05-16 07:51:08Payjoin allows the sender and receiver of an on-chain payment to collaborate and create a transaction that breaks on-chain heuristics, allowing a more private transaction with ambiguous payment amount and UTXO ownership. Additionally, it can also be used for UTXO consolidation (receiver saves future fees) and batching payments (receiver can make payment(s) of their own in the process of receiving one), also known as transaction cut-through. Other than improved privacy, the rest of the benefits are typically applicable to the receiver, not the sender.
BIP-78 was the original payjoin protocol that required the receiver to run a endpoint/server (always online) in order to mediate the payjoin process. Payjoin adoption has remained pretty low, something attributed to the server & perpetual online-ness requirement. This is the motivation for payjoin v2.
The purpose of the one-pager is to analyse the protocol, and highlight the UX issues or tradeoffs it entails, so that the payjoin user flows can be appropriately designed and the tradeoffs likewise communicated. A further document on UX solutions might be needed to identify solutions and opportunities
The following observations are generally limited to individual users transacting through their mobile devices:
While users naturally want better privacy and fee-savings, they also want to minimise friction and minimise (optimise) payment time. These are universal and more immediate needs since they deal with the user experience.
Added manual steps
TL;DR v2 payjoin eliminates server & simultaneous user-liveness requirements (increasing TAM, and opportunities to payjoin, as a result) by adding manual steps.
Usually, the extent of the receiver's involvement in the transaction process is limited to sharing their address with the sender. Once they share the address/URI, they can basically forget about it. In the target scenario for v2 payjoin, the receiver must come online again (except they have no way of knowing "when") to contribute input(s) and sign the PSBT. This can be unexpected, unintuitive and a bit of a hassle.
Usually (and even with payjoin v1), the sender crafts and broadcasts the transaction in one go; meaning the user's job is done within a few seconds/minutes. With payjoin v2, they must share the original-PSBT with the receiver, and then wait for them to do their part. Once the the receiver has done that, the sender must come online to review the transaction, sign it & broadcast.
In summary,
In payjoin v1, step 3 is automated and instant, so delay 2, 3 =~ 0. As the user experiences it, the process is completed in a single session, akin to a non-payjoin transaction.
With payjoin v2, Steps 2 & 3 in the above diagram are widely spread and noticeable. These manual steps are separated by uncertain delays (more on that below) when compared to a non-payjoin transaction.
Delays
We've established that both senders and receivers must take extra manual steps to execute a payoin transaction. With payjoin v2, this process gets split into multiple sessions, since the sender and receiver are not like to be online simultaneously.
Delay 2 & 3 (see diagram above) are uncertain in nature. Most users do not open their bitcoin wallets for days or weeks! The receiver must come online before the timeout hits in order for the payjoin process to work, otherwise time is just wasted with no benefit. UX or technical solutions are needed to minimise these delays.
Delays might be exacerbated if the setup is based on hardware wallet and/or uses multisig.
Notifications or background processes
There is one major problem when we say "the user must come online to..." but in reality the user has no way of knowing there is a payjoin PSBT waiting for them. After a PSBT is sent to the relay, the opposite user would only find out about it whenever they happen to come online. Notifications and background sync processes might be necessary to minimise delays. This is absolutely essential to avert timeouts in addition to saving valuable time. Another risk is phantom payjoin stuff after the timeout is expired if receiver-side does not know it has.
Fee Savings
The following observations might be generally applicable for both original and this v2 payjoin version. Fee-savings with payjoin is a tricky topic. Of course, overall a payjoin transaction is always cheaper than 2 separate transactions, since they get to share the overhead.
Additionally, without the receiver contributing to fees, the chosen fee rate of the PSBT (at the beginning) drops, and can lead to slower confirmation. From another perspective, a sender paying with payjoin pays higher fees for similar confirmation target. This has been observed in a production wallet years back. Given that total transaction time can extend to days, the fee environment itself might change, and all this must be considered when designing the UX.
Of course, there is nothing stopping the receiver from contributing to fees, but this idea is likely entirely novel to the bitcoin ecosystem (perhaps payments ecosystem in general) and the user base. Additionally, nominally it involves the user paying fees and tolerating delays just to receive bitcoin. Without explicit incentives/features that encourage receivers to participate, payjoining might seem like an unncessary hassle.
Overall, it seems that payjoin makes UX significant tradeoffs for important privacy (and potential fee-saving) benefits. This means that the UX might have to do significant heavy-lifting, to ensure that users are not surprised, confused or frustrated when they try to transact on-chain in a privacy-friendly feature. Good, timely communication, new features for consolidation & txn-cutthrough and guided user flows seem crucial to ensure payjoin adoption and for help make on-chain privacy a reality for users.
---------------
Original document available here. Reach out at
yashrajdca@proton.me,y_a_s_h_r_a_j.70on Signal, or on reach out in Bitcoin Design discord.https://stacker.news/items/981388
-
 @ 0b118e40:4edc09cb
2025-04-13 02:46:36
@ 0b118e40:4edc09cb
2025-04-13 02:46:36note - i wrote this before the global trade war, back when tariffs only affected China, Mexico, and Canada. But you will still get the gist of it.
During tough economic times, governments have to decide if they should open markets to global trade or protect local businesses with tariffs. The United States has swung between these two strategies, and history shows that the results are never straightforward
Just days ago, President Donald Trump imposed tariffs on imports from Canada, Mexico, and China. He framed these tariffs (25% on most Canadian goods, 10% on Canadian energy, 25% on Mexican imports, and 10% on Chinese imports) as a way to protect American industries.
But will they actually help, or could they backfire?
A History of U.S. Tariffs
Many have asked if countries will retaliate against the US. They can and they have. Once upon a time, 60 countries were so pissed off at the US, they retaliated at one go and crushed US dominance over trade.
This was during the Great Depression era in the 1930s when the government passed the Smoot-Hawley Tariff Act, placing high taxes on over 20,000 foreign goods. The goal was to protect American jobs, especially American farmers and manufacturers, but it backfired so badly.
Over 60 countries, including Canada, France, and Germany, retaliated by imposing their own tariffs. By 1933, US imports and exports both dropped significantly over 60%, and unemployment rose to 25%.
After President Franklin Roosevelt came to office, he implemented the Reciprocal Trade Agreements Act of 1934 to reverse these policies, calming the world down and reviving trade again.
The economist history of protectionism
The idea of shielding local businesses with tariffs isn’t new or recent. It's been around for a few centuries. In the 16th to 18th centuries, mercantilism encouraged countries to limit imports and boost exports.
In the 18th century, Adam Smith, in The Wealth of Nations, argued that free trade allows nations to specialize in what they do best countering protectionism policies. Friedrich List later challenged Smith's view by stating that developing countries need some protection to grow their “infant” industries which is a belief that still influences many governments today.
But how often do governments truly support startups and new small businesses in ways that create real growth, rather than allowing funds to trickle down to large corporations instead?
In modern times, John Maynard Keynes supported government intervention during economic downturns, while Milton Friedman championed free trade and minimal state interference.
Paul Krugman argued that limited protectionism can help large industries by providing them unfair advantages to become global market leaders. I have deep reservations about Krugman’s take, particularly on its impact or lack thereof in globalizing small businesses.
The debate between free trade and protectionism has existed for centuries. What’s clear is that there is no one-size-fits-all model to this.
The Political Debate - left vs right
Both the left and right have used tariffs but for different reasons. The right supports tariffs to protect jobs and industries, while the left uses them to prevent multinational corporations from exploiting cheap labor abroad.
Neoliberal policies favor free trade, arguing that competition drives efficiency and growth. In the US this gets a little bit confusing as liberals are tied to the left, and free trade is tied to libertarianism which the rights align closely with, yet at present right wing politicians push for protectionism which crosses the boundaries of free-trade.
There are also institutions like the WTO and IMF who advocate for open markets, but their policies often reflect political alliances and preferential treatment - so it depends on what you define as true 'free trade’.
Who Really Benefits from Tariffs?
Most often, tariffs help capital-intensive industries like pharmaceuticals, tech, and defense, while hurting labor-intensive sectors like manufacturing, agriculture, and construction.
This worsens inequality as big corporations will thrive, while small businesses and working-class people struggle with rising costs and fewer job opportunities.
I’ve been reading through international trade economics out of personal interest, I'll share some models below on why this is the case
1. The Disruption of Natural Trade
Tariffs disrupt the natural flow of trade. The Heckscher-Ohlin model explains that countries export goods that match their resources like Canada’s natural resource energy or China’s labour intensive textile and electronics. When tariffs block this natural exchange, industries suffer.
A clear example was Europe’s energy crisis during the Russia-Ukraine war. By abruptly cutting themselves off from the supply of Russian energy, Europe scrambled to find alternative sources. In the end, it was the people who had to bear the brunt of skyrocketing prices of energy.
2. Who wins and who loses?
The Stolper-Samuelson theorem helps us understand who benefits from tariffs and who loses. The idea behind it is that tariffs benefit capital-intensive industries, while labor-intensive sectors are hurt.
In the US, small manufacturing industries that rely on low-cost imports on intermediary parts from countries like China and Mexico will face rising costs, making their final goods too expensive and less competitive. This is similar to what happened to Argentina, where subsidies and devaluation of pesos contributed to cost-push inflation, making locally produced goods more expensive and less competitive globally.
This also reminded me of the decline of the US Rust Belt during the 1970s and 1980s, where the outsourcing of labour-intensive manufacturing jobs led to economic stagnation in many regions in the Midwest, while capital-intensive sectors flourished on the coasts. It resulted in significantly high income inequality that has not improved over the last 40 years.
Ultimately the cost of economic disruption is disproportionately borne by smaller businesses and low-skilled workers. At the end of the day, the rich get richer and the poor get poorer.
3. Delays in Economic Growth
The Rybczynski theorem suggests that economic growth depends on how efficiently nations reallocate their resources toward capital- or labor-intensive industries. But tariffs can distort this transition and progress.
In the 70s and 80s, the US steel industry had competition from Japan and Germany who modernized their production methods, making their steel more efficient and cost-effective. Instead of prioritizing innovation, many U.S. steel producers relied on tariffs and protectionist measures to shield themselves from foreign competition. This helped for a bit but over time, American steelmakers lost global market share as foreign competitors continued to produce better, cheaper steel. Other factors, such as aging infrastructure, and economic shifts toward a service-based economy, further contributed to the industry's decline.
A similar struggle is seen today with China’s high-tech ambitions. Tariffs on Chinese electronics and technology products limit access to key inputs, such as semiconductors and advanced robotics. While China continues its push for automation and AI-driven manufacturing, these trade barriers increase costs and disrupt supply chains, forcing China to accelerate its decoupling from Western markets. This shift could further strengthen alliances within BRICS, as China seeks alternative trade partnerships to reduce reliance on U.S.-controlled financial and technological ecosystems.
Will the current Tariff imposition backfire and isolate the US like it did a hundred years ago or 50 years ago? Is US risking it's position as a trusted economic leader? Only time would tell
The impact of tariff on innovation - or lack thereof
While the short-term impacts of tariffs often include higher consumer prices and job losses, the long-term effects can be even more damaging, as they discourage innovation by increasing costs and reducing competition.
Some historical examples globally : * Nigeria: Blocking import of rice opened up black market out of desperation to survive. * Brazil: Protectionist car policies led to expensive, outdated vehicles. * Malaysia’s Proton: Sheltered by tariffs and cronyism and failed to compete globally. * India (before 1991): Over-regulation limited the industries, until economic reforms allowed for growth. * Soviet Union during Cold War : Substandard products and minimal innovation due to the absence of foreign alternatives, yielding to economic stagnation.
On the flip side, Vietnam has significantly reduced protectionism policies by actively pursuing free trade agreements. This enabled it to become a key manufacturing hub. But Vietnam is not stopping there as it is actively pushing forward its capital-intensive growth by funding entrepreneurs.
The Future of U.S. Tariffs
History has shown that tariffs rarely deliver their intended benefits without unintended consequences. While they may provide temporary relief, they often raise prices, shrink job opportunities, and weaken industries in the long run.
Without a clear strategy for innovation and industrial modernization, the U.S. risks repeating past mistakes of isolating itself from global trade rather than strengthening its economy.
At this point, only time will tell whether these tariffs will truly help Americans or will they, once again, make the rich richer and the poor poorer.
-
 @ 3b3a42d3:d192e325
2025-04-10 08:57:51
@ 3b3a42d3:d192e325
2025-04-10 08:57:51Atomic Signature Swaps (ASS) over Nostr is a protocol for atomically exchanging Schnorr signatures using Nostr events for orchestration. This new primitive enables multiple interesting applications like:
- Getting paid to publish specific Nostr events
- Issuing automatic payment receipts
- Contract signing in exchange for payment
- P2P asset exchanges
- Trading and enforcement of asset option contracts
- Payment in exchange for Nostr-based credentials or access tokens
- Exchanging GMs 🌞
It only requires that (i) the involved signatures be Schnorr signatures using the secp256k1 curve and that (ii) at least one of those signatures be accessible to both parties. These requirements are naturally met by Nostr events (published to relays), Taproot transactions (published to the mempool and later to the blockchain), and Cashu payments (using mints that support NUT-07, allowing any pair of these signatures to be swapped atomically.
How the Cryptographic Magic Works 🪄
This is a Schnorr signature
(Zₓ, s):s = z + H(Zₓ || P || m)⋅kIf you haven't seen it before, don't worry, neither did I until three weeks ago.
The signature scalar s is the the value a signer with private key
k(and public keyP = k⋅G) must calculate to prove his commitment over the messagemgiven a randomly generated noncez(Zₓis just the x-coordinate of the public pointZ = z⋅G).His a hash function (sha256 with the tag "BIP0340/challenge" when dealing with BIP340),||just means to concatenate andGis the generator point of the elliptic curve, used to derive public values from private ones.Now that you understand what this equation means, let's just rename
z = r + t. We can do that,zis just a randomly generated number that can be represented as the sum of two other numbers. It also follows thatz⋅G = r⋅G + t⋅G ⇔ Z = R + T. Putting it all back into the definition of a Schnorr signature we get:s = (r + t) + H((R + T)ₓ || P || m)⋅kWhich is the same as:
s = sₐ + twheresₐ = r + H((R + T)ₓ || P || m)⋅ksₐis what we call the adaptor signature scalar) and t is the secret.((R + T)ₓ, sₐ)is an incomplete signature that just becomes valid by add the secret t to thesₐ:s = sₐ + tWhat is also important for our purposes is that by getting access to the valid signature s, one can also extract t from it by just subtracting
sₐ:t = s - sₐThe specific value of
tdepends on our choice of the public pointT, sinceRis just a public point derived from a randomly generated noncer.So how do we choose
Tso that it requires the secret t to be the signature over a specific messagem'by an specific public keyP'? (without knowing the value oft)Let's start with the definition of t as a valid Schnorr signature by P' over m':
t = r' + H(R'ₓ || P' || m')⋅k' ⇔ t⋅G = r'⋅G + H(R'ₓ || P' || m')⋅k'⋅GThat is the same as:
T = R' + H(R'ₓ || P' || m')⋅P'Notice that in order to calculate the appropriate
Tthat requirestto be an specific signature scalar, we only need to know the public nonceR'used to generate that signature.In summary: in order to atomically swap Schnorr signatures, one party
P'must provide a public nonceR', while the other partyPmust provide an adaptor signature using that nonce:sₐ = r + H((R + T)ₓ || P || m)⋅kwhereT = R' + H(R'ₓ || P' || m')⋅P'P'(the nonce provider) can then add his own signature t to the adaptor signaturesₐin order to get a valid signature byP, i.e.s = sₐ + t. When he publishes this signature (as a Nostr event, Cashu transaction or Taproot transaction), it becomes accessible toPthat can now extract the signaturetbyP'and also make use of it.Important considerations
A signature may not be useful at the end of the swap if it unlocks funds that have already been spent, or that are vulnerable to fee bidding wars.
When a swap involves a Taproot UTXO, it must always use a 2-of-2 multisig timelock to avoid those issues.
Cashu tokens do not require this measure when its signature is revealed first, because the mint won't reveal the other signature if they can't be successfully claimed, but they also require a 2-of-2 multisig timelock when its signature is only revealed last (what is unavoidable in cashu for cashu swaps).
For Nostr events, whoever receives the signature first needs to publish it to at least one relay that is accessible by the other party. This is a reasonable expectation in most cases, but may be an issue if the event kind involved is meant to be used privately.
How to Orchestrate the Swap over Nostr?
Before going into the specific event kinds, it is important to recognize what are the requirements they must meet and what are the concerns they must address. There are mainly three requirements:
- Both parties must agree on the messages they are going to sign
- One party must provide a public nonce
- The other party must provide an adaptor signature using that nonce
There is also a fundamental asymmetry in the roles of both parties, resulting in the following significant downsides for the party that generates the adaptor signature:
- NIP-07 and remote signers do not currently support the generation of adaptor signatures, so he must either insert his nsec in the client or use a fork of another signer
- There is an overhead of retrieving the completed signature containing the secret, either from the blockchain, mint endpoint or finding the appropriate relay
- There is risk he may not get his side of the deal if the other party only uses his signature privately, as I have already mentioned
- There is risk of losing funds by not extracting or using the signature before its timelock expires. The other party has no risk since his own signature won't be exposed by just not using the signature he received.
The protocol must meet all those requirements, allowing for some kind of role negotiation and while trying to reduce the necessary hops needed to complete the swap.
Swap Proposal Event (kind:455)
This event enables a proposer and his counterparty to agree on the specific messages whose signatures they intend to exchange. The
contentfield is the following stringified JSON:{ "give": <signature spec (required)>, "take": <signature spec (required)>, "exp": <expiration timestamp (optional)>, "role": "<adaptor | nonce (optional)>", "description": "<Info about the proposal (optional)>", "nonce": "<Signature public nonce (optional)>", "enc_s": "<Encrypted signature scalar (optional)>" }The field
roleindicates what the proposer will provide during the swap, either the nonce or the adaptor. When this optional field is not provided, the counterparty may decide whether he will send a nonce back in a Swap Nonce event or a Swap Adaptor event using thenonce(optionally) provided by in the Swap Proposal in order to avoid one hop of interaction.The
enc_sfield may be used to store the encrypted scalar of the signature associated with thenonce, since this information is necessary later when completing the adaptor signature received from the other party.A
signature specspecifies thetypeand all necessary information for producing and verifying a given signature. In the case of signatures for Nostr events, it contain a template with all the fields, exceptpubkey,idandsig:{ "type": "nostr", "template": { "kind": "<kind>" "content": "<content>" "tags": [ … ], "created_at": "<created_at>" } }In the case of Cashu payments, a simplified
signature specjust needs to specify the payment amount and an array of mints trusted by the proposer:{ "type": "cashu", "amount": "<amount>", "mint": ["<acceptable mint_url>", …] }This works when the payer provides the adaptor signature, but it still needs to be extended to also work when the payer is the one receiving the adaptor signature. In the later case, the
signature specmust also include atimelockand the derived public keysYof each Cashu Proof, but for now let's just ignore this situation. It should be mentioned that the mint must be trusted by both parties and also support Token state check (NUT-07) for revealing the completed adaptor signature and P2PK spending conditions (NUT-11) for the cryptographic scheme to work.The
tagsare:"p", the proposal counterparty's public key (required)"a", akind:30455Swap Listing event or an application specific version of it (optional)
Forget about this Swap Listing event for now, I will get to it later...
Swap Nonce Event (kind:456) - Optional
This is an optional event for the Swap Proposal receiver to provide the public nonce of his signature when the proposal does not include a nonce or when he does not want to provide the adaptor signature due to the downsides previously mentioned. The
contentfield is the following stringified JSON:{ "nonce": "<Signature public nonce>", "enc_s": "<Encrypted signature scalar (optional)>" }And the
tagsmust contain:"e", akind:455Swap Proposal Event (required)"p", the counterparty's public key (required)
Swap Adaptor Event (kind:457)
The
contentfield is the following stringified JSON:{ "adaptors": [ { "sa": "<Adaptor signature scalar>", "R": "<Signer's public nonce (including parity byte)>", "T": "<Adaptor point (including parity byte)>", "Y": "<Cashu proof derived public key (if applicable)>", }, …], "cashu": "<Cashu V4 token (if applicable)>" }And the
tagsmust contain:"e", akind:455Swap Proposal Event (required)"p", the counterparty's public key (required)
Discoverability
The Swap Listing event previously mentioned as an optional tag in the Swap Proposal may be used to find an appropriate counterparty for a swap. It allows a user to announce what he wants to accomplish, what his requirements are and what is still open for negotiation.
Swap Listing Event (kind:30455)
The
contentfield is the following stringified JSON:{ "description": "<Information about the listing (required)>", "give": <partial signature spec (optional)>, "take": <partial signature spec (optional)>, "examples: [<take signature spec>], // optional "exp": <expiration timestamp (optional)>, "role": "<adaptor | nonce (optional)>" }The
descriptionfield describes the restrictions on counterparties and signatures the user is willing to accept.A
partial signature specis an incompletesignature specused in Swap Proposal eventskind:455where omitting fields signals that they are still open for negotiation.The
examplesfield is an array ofsignature specsthe user would be willing totake.The
tagsare:"d", a unique listing id (required)"s", the status of the listingdraft | open | closed(required)"t", topics related to this listing (optional)"p", public keys to notify about the proposal (optional)
Application Specific Swap Listings
Since Swap Listings are still fairly generic, it is expected that specific use cases define new event kinds based on the generic listing. Those application specific swap listing would be easier to filter by clients and may impose restrictions and add new fields and/or tags. The following are some examples under development:
Sponsored Events
This listing is designed for users looking to promote content on the Nostr network, as well as for those who want to monetize their accounts by sharing curated sponsored content with their existing audiences.
It follows the same format as the generic Swap Listing event, but uses the
kind:30456instead.The following new tags are included:
"k", event kind being sponsored (required)"title", campaign title (optional)
It is required that at least one
signature spec(giveand/ortake) must have"type": "nostr"and also contain the following tag["sponsor", "<pubkey>", "<attestation>"]with the sponsor's public key and his signature over the signature spec without the sponsor tag as his attestation. This last requirement enables clients to disclose and/or filter sponsored events.Asset Swaps
This listing is designed for users looking for counterparties to swap different assets that can be transferred using Schnorr signatures, like any unit of Cashu tokens, Bitcoin or other asset IOUs issued using Taproot.
It follows the same format as the generic Swap Listing event, but uses the
kind:30457instead.It requires the following additional tags:
"t", asset pair to be swapped (e.g."btcusd")"t", asset being offered (e.g."btc")"t", accepted payment method (e.g."cashu","taproot")
Swap Negotiation
From finding an appropriate Swap Listing to publishing a Swap Proposal, there may be some kind of negotiation between the involved parties, e.g. agreeing on the amount to be paid by one of the parties or the exact content of a Nostr event signed by the other party. There are many ways to accomplish that and clients may implement it as they see fit for their specific goals. Some suggestions are:
- Adding
kind:1111Comments to the Swap Listing or an existing Swap Proposal - Exchanging tentative Swap Proposals back and forth until an agreement is reached
- Simple exchanges of DMs
- Out of band communication (e.g. Signal)
Work to be done
I've been refining this specification as I develop some proof-of-concept clients to experience its flaws and trade-offs in practice. I left the signature spec for Taproot signatures out of the current document as I still have to experiment with it. I will probably find some important orchestration issues related to dealing with
2-of-2 multisig timelocks, which also affects Cashu transactions when spent last, that may require further adjustments to what was presented here.The main goal of this article is to find other people interested in this concept and willing to provide valuable feedback before a PR is opened in the NIPs repository for broader discussions.
References
- GM Swap- Nostr client for atomically exchanging GM notes. Live demo available here.
- Sig4Sats Script - A Typescript script demonstrating the swap of a Cashu payment for a signed Nostr event.
- Loudr- Nostr client under development for sponsoring the publication of Nostr events. Live demo available at loudr.me.
- Poelstra, A. (2017). Scriptless Scripts. Blockstream Research. https://github.com/BlockstreamResearch/scriptless-scripts
-
 @ eb0157af:77ab6c55
2025-05-16 07:32:01
@ eb0157af:77ab6c55
2025-05-16 07:32:01The bank’s analysts are observing a shift in the Bitcoin market, with specific catalysts that could drive the cryptocurrency higher.
According to a recent JPMorgan report shared with select industry outlets, Bitcoin could continue its rise at the expense of gold in the second half of 2025. Analysts led by Managing Director Nikolaos Panigirtzoglou highlighted that the so-called “debasement trade” — the strategy of investing in gold and Bitcoin as a hedge against the weakening of fiat currencies — has undergone a change in direction.
“What began as a parallel run has turned into a zero-sum game between the two assets,” the analysts explained. “Between mid-February and mid-April, gold rallied at Bitcoin’s expense, while over the past three weeks we’ve seen the opposite: Bitcoin rising as gold loses ground.”
Since its peak on April 22, gold has declined by nearly 8%, while over the same period, Bitcoin has gained 18%. This shift is also reflected in investor flows, with capital moving out of gold ETFs and into spot Bitcoin ETFs.
Futures market data shows a similar trend, with declining positions in gold and increasing interest in Bitcoin futures. Notably, at the start of the year, the situation was completely reversed, with gold rallying while Bitcoin struggled alongside other risk assets.
Specific catalysts driving Bitcoin’s growth
The report emphasizes that Bitcoin’s recent outperformance is not solely due to gold’s weakness but also driven by sector-specific factors:
- Companies like Strategy and Metaplanet are increasing their Bitcoin purchases. Strategy, in particular, plans to raise an additional $84 billion for acquisitions by 2027, having already reached 60% of its original target.
- Some U.S. states have begun adding Bitcoin to their reserves. New Hampshire now allows up to 5% of state assets to be invested in Bitcoin and gold.
“As more U.S. states consider adding Bitcoin to their strategic reserves, this could prove to be a sustained positive catalyst for Bitcoin,” the analysts wrote. Given the weakening of gold prices and these industry-specific drivers, JPMorgan’s analysts see greater growth potential for Bitcoin in the second half of the year.
The post Bitcoin outperforming gold in the second half of 2025: JPMorgan appeared first on Atlas21.
-
 @ 57d1a264:69f1fee1
2025-05-16 05:38:28
@ 57d1a264:69f1fee1
2025-05-16 05:38:28LegoGPT generates a LEGO structure from a user-provided text prompt in an end-to-end manner. Notably, our generated LEGO structure is physically stable and buildable.
Lego is something most of us knows. This is a opportuity to ask where is our creativity going? From the art of crafting figures to building blocks following our need and desires to have a machine thinking and building following step-by-step instructions to achieve an isolated goal.
Is the creative act then in the question itself, not anymore in the crafting? Are we just delegating the solution of problems, the thinking of how to respond to questions, to machines? Would it be different if delegated to other people?
Source: https://avalovelace1.github.io/LegoGPT/
https://stacker.news/items/981336
-
 @ 4fe4a528:3ff6bf06
2025-05-16 04:36:31
@ 4fe4a528:3ff6bf06
2025-05-16 04:36:31One of the main motivational factors for people to buy bitcoin is it’s ability to store value over time. During harvest we are doing the same thing. We have now harvested our garlic and 1/2 of our onions because if we don’t use the sun’s energy to cure the plants before winter they will start to rot. Let me explain why God has made the world this way; but, first let me explain why storing things isn’t evil.
“Do not store up for yourselves treasures on earth, where moth and rust consume and where thieves break in and steal; but store up for yourselves treasures in heaven, where neither moth nor rust consumes and where thieves do not break in and steal. For where your treasure is, there your heart will be also”. Matt. 6:19-21
Is it wrong, then to have a retirement portfolio or even to care about the material things of this world for ourselves or for others? The answer is again both no and yes. The no comes from the fact that this passage is not the only one in the Bible speaking to questions of wealth and provision for those who are dependent on us. Other passages counsel prudence and forethought, such as, “Those who gather little by little will increase [wealth]” (Proverbs 13:11b), and, “The good leave an inheritance to their children’s children” (Proverbs 13:22).
God guides Joseph to store up food for seven years in advance of a famine (Genesis 41:25-36), and Jesus speaks favorably in the Parable of the Talents (Matt. 25:14-30). In light of the rest of Scripture, Matthew 6:19-21 cannot be a blanket prohibition. But the yes part of the answer is a warning, summed up beautifully in verse 21, “Where your treasure is, there will your heart be also.” In other words, the possessions you own will change you so that you care more about the possessions than about other things.” So choose carefully what you own, for you will inevitably begin to value and protect it to the potential detriment of everything else.
How are we to discern the line between appropriate and inappropriate attention to wealth? Jesus answers, “Strive first for the kingdom of God and his righteousness, and all these things will be given to you” So if you believe your heart is following God’s direction go ahead and harvest your crops and / or buy some bitcoin. If you would have bought bitcoin one year ago, you would have 127% more purchasing power now. Let’s keep on fearing God and keeping his commandments.
-
 @ 66675158:1b644430
2025-03-23 11:39:41
@ 66675158:1b644430
2025-03-23 11:39:41I don't believe in "vibe coding" – it's just the newest Silicon Valley fad trying to give meaning to their latest favorite technology, LLMs. We've seen this pattern before with blockchain, when suddenly Non Fungible Tokens appeared, followed by Web3 startups promising to revolutionize everything from social media to supply chains. VCs couldn't throw money fast enough at anything with "decentralized" (in name only) in the pitch deck. Andreessen Horowitz launched billion-dollar crypto funds, while Y Combinator batches filled with blockchain startups promising to be "Uber for X, but on the blockchain."
The metaverse mania followed, with Meta betting its future on digital worlds where we'd supposedly hang out as legless avatars. Decentralized (in name only) autonomous organizations emerged as the next big thing – supposedly democratic internet communities that ended up being the next scam for quick money.
Then came the inevitable collapse. The FTX implosion in late 2022 revealed fraud, Luna/Terra's death spiral wiped out billions (including my ten thousand dollars), while Celsius and BlockFi froze customer assets before bankruptcy.
By 2023, crypto winter had fully set in. The SEC started aggressive enforcement actions, while users realized that blockchain technology had delivered almost no practical value despite a decade of promises.
Blockchain's promises tapped into fundamental human desires – decentralization resonated with a generation disillusioned by traditional institutions. Evangelists presented a utopian vision of freedom from centralized control. Perhaps most significantly, crypto offered a sense of meaning in an increasingly abstract world, making the clear signs of scams harder to notice.
The technology itself had failed to solve any real-world problems at scale. By 2024, the once-mighty crypto ecosystem had become a cautionary tale. Venture firms quietly scrubbed blockchain references from their websites while founders pivoted to AI and large language models.
Most reading this are likely fellow bitcoiners and nostr users who understand that Bitcoin is blockchain's only valid use case. But I shared that painful history because I believe the AI-hype cycle will follow the same trajectory.
Just like with blockchain, we're now seeing VCs who once couldn't stop talking about "Web3" falling over themselves to fund anything with "AI" in the pitch deck. The buzzwords have simply changed from "decentralized" to "intelligent."
"Vibe coding" is the perfect example – a trendy name for what is essentially just fuzzy instructions to LLMs. Developers who've spent years honing programming skills are now supposed to believe that "vibing" with an AI is somehow a legitimate methodology.
This might be controversial to some, but obvious to others:
Formal, context-free grammar will always remain essential for building precise systems, regardless of how advanced natural language technology becomes
The mathematical precision of programming languages provides a foundation that human language's ambiguity can never replace. Programming requires precision – languages, compilers, and processors operate on explicit instructions, not vibes. What "vibe coding" advocates miss is that beneath every AI-generated snippet lies the same deterministic rules that have always governed computation.
LLMs don't understand code in any meaningful sense—they've just ingested enormous datasets of human-written code and can predict patterns. When they "work," it's because they've seen similar patterns before, not because they comprehend the underlying logic.
This creates a dangerous dependency. Junior developers "vibing" with LLMs might get working code without understanding the fundamental principles. When something breaks in production, they'll lack the knowledge to fix it.
Even experienced developers can find themselves in treacherous territory when relying too heavily on LLM-generated code. What starts as a productivity boost can transform into a dependency crutch.
The real danger isn't just technical limitations, but the false confidence it instills. Developers begin to believe they understand systems they've merely instructed an AI to generate – fundamentally different from understanding code you've written yourself.
We're already seeing the warning signs: projects cobbled together with LLM-generated code that work initially but become maintenance nightmares when requirements change or edge cases emerge.
The venture capital money is flowing exactly as it did with blockchain. Anthropic raised billions, OpenAI is valued astronomically despite minimal revenue, and countless others are competing to build ever-larger models with vague promises. Every startup now claims to be "AI-powered" regardless of whether it makes sense.
Don't get me wrong—there's genuine innovation happening in AI research. But "vibe coding" isn't it. It's a marketing term designed to make fuzzy prompting sound revolutionary.
Cursor perfectly embodies this AI hype cycle. It's an AI-enhanced code editor built on VS Code that promises to revolutionize programming by letting you "chat with your codebase." Just like blockchain startups promised to "revolutionize" industries, Cursor promises to transform development by adding LLM capabilities.
Yes, Cursor can be genuinely helpful. It can explain unfamiliar code, suggest completions, and help debug simple issues. After trying it for just an hour, I found the autocomplete to be MAGICAL for simple refactoring and basic functionality.
But the marketing goes far beyond reality. The suggestion that you can simply describe what you want and get production-ready code is dangerously misleading. What you get are approximations with:
- Security vulnerabilities the model doesn't understand
- Edge cases it hasn't considered
- Performance implications it can't reason about
- Dependency conflicts it has no way to foresee
The most concerning aspect is how such tools are marketed to beginners as shortcuts around learning fundamentals. "Why spend years learning to code when you can just tell AI what you want?" This is reminiscent of how crypto was sold as a get-rich-quick scheme requiring no actual understanding.
When you "vibe code" with an AI, you're not eliminating complexity—you're outsourcing understanding to a black box. This creates developers who can prompt but not program, who can generate but not comprehend.
The real utility of LLMs in development is in augmenting existing workflows:
- Explaining unfamiliar codebases
- Generating boilerplate for well-understood patterns
- Suggesting implementations that a developer evaluates critically
- Assisting with documentation and testing
These uses involve the model as a subordinate assistant to a knowledgeable developer, not as a replacement for expertise. This is where the technology adds value—as a sophisticated tool in skilled hands.
Cursor is just a better hammer, not a replacement for understanding what you're building. The actual value emerges when used by developers who understand what happens beneath the abstractions. They can recognize when AI suggestions make sense and when they don't because they have the fundamental knowledge to evaluate output critically.
This is precisely where the "vibe coding" narrative falls apart.
-
 @ 7b20d99d:d2a541a9
2025-05-16 04:03:23
@ 7b20d99d:d2a541a9
2025-05-16 04:03:23In a world where we often hear talk of financial bubbles, speculation, and individual enrichment through cryptocurrencies, Hope With Bitcoin resolutely takes the opposite approach. Here, Bitcoin is not an end in itself, but a means to reach out. A tool serving a simple, universal human cause: bringing smiles and hope back to those who need it most.
Far from big, empty promises and empty charitable projects, Hope With Bitcoin is committed to a philosophy of direct impact, total transparency, and lasting transformation of lives.
🔗 Official project link : https://linktr.ee/hopewithbtc
🟢 Why “Hope With Bitcoin”?
It all started with an observation: too many people are living in oblivion. In some regions, particularly in Africa, it doesn't take much to bring back a smile: a meal, a word, a gesture. But often, aid initiatives get lost in an administrative maze, corruption, or a lack of follow-ups. And in the world of Bitcoin, we see many promises of humanitarian aid without ever seeing results.
Hope With Bitcoin was launched to change that. The goal is clear:
Using the power of Bitcoin to provide direct, visible, measurable and lasting help.
We wanted to show that Bitcoin can nourish, heal, raise awareness, connect, and not just speculate.
🔵 What we do concretely
Hope With Bitcoin isn't an abstract concept. It's a set of concrete actions carried out on the ground, with rigor and heart.
Here's what we do:
🍛 Food distribution and health aid
Thanks to donations collected in Bitcoin, we provide concrete help to those who need it most.
We distribute hot meals and basic food items (rice, spaghetti, oil, charcoal, etc.) to struggling families, vulnerable children, and orphanages.
But our work doesn't stop there. A portion of the funds is also used to purchase essential medicines and contribute to the payment of healthcare, particularly for sick or injured people who cannot afford treatment.
Each action is carefully documented and made public to ensure complete transparency and strengthen the trust of our donors.
✅ Missions accomplished: every satoshi counts
Since Hope With Bitcoin's inception, we've carried out several concrete actions thanks to the donations received. Here's a clear, transparent, and verifiable overview of our actions:
🔹 PoW 1 – 10 000 Satoshi Received
📅 Date : 01/09/2025
📍 Purchase food for two children in need
🔹 PoW 2 – 10 000 Satoshi Received
📅 Date : 01/11/2025
📍 Purchase food for two children in need


🔹 PoW 3 — 220,500 Satoshi received
📍 Preparing food for thirty children in need
📅 Date : 01/13/2025

🔹 PoW 4— 31,000 Satoshi received
📍 Purchase food for six children in need
📅 Date : 01/16/2025

🔹 PoW 5— 30,000 Satoshi received
📍 Purchase food for 10 students in need
📅 Date : 01/18/2025

🔹 PoW 6 – 11,093 Satoshi received
📍 Purchase food for two children in need
📅 Date : 01/22/2025
 #### \
🔹 PoW 7 – 52,000 Satoshi Received
#### \
🔹 PoW 7 – 52,000 Satoshi Received📍 Preparing food for eight children in need
📅 Date : 01/27/2025
 #### \
🔹 PoW 8 – 116,866 Satoshi Received
#### \
🔹 PoW 8 – 116,866 Satoshi Received📍Financial support for Maria Jimenez's health
📅 Date : 02/13/2025

🔹 PoW 9 – 8,001 Satoshi Received
📍 Hope With Bitcoin t-shirt print
📅 Date : 02/15/2025


🔹 PoW 10 – 22,602 Satoshi Received
📍 Purchase of food for five children in need (three on site and two takeaway)
📅 Date : 02/17/2025

🔹 PoW 11– 350,000 Satoshi Received
📍 Purchase of food (rice, corn, spaghetti, oil, salt, sugar, coal...) at the Bon Arbre orphanage
Thank you letter received: HERE
📅 Date : 03/06/2025

🔹 PoW 12 – 35,000 Satoshi received
📍 Purchase of medicine for a person in need
📅 Date : 04/02/2025

🔹 PoW 13 – 60,910 Satoshi received
📍 Purchase food for two children in need
🖼 Coming soon
📅 Date : 05/18/2025
Each of these Proofs of Work (PoW) is publicly published on Nostr or Geyser to ensure complete transparency. You can view them individually to see the real impact of your donations.
📣 Bitcoin Adoption Awareness
We take advantage of each field trip to speak with shopkeepers, local vendors, and young people. The idea is to show that Bitcoin can be used practically in their daily lives: to sell, buy, and exchange.
🟠 Our results to date
Since the creation of Hope With Bitcoin on January 8, 2025, we have succeeded in:
- Collect a total of 957,971 Satoshi thanks to the generosity of contributors around the world.
- Help 87 people directly through our distribution actions. (Proof of work)
- Raise awareness among several merchants about the use of Bitcoin.
- Create a close-knit, caring community focused on human impact.
These numbers aren't statistics. They're lives, faces, stories. Every person helped represents a victory, proof that Bitcoin solidarity is possible.
🟣 Our ambitions for the future
Hope With Bitcoin doesn't want to be just a one-time donation project. We believe in sustainability, independence, and structured growth.
### 🐖 Launch of a pig farm to sustainably finance our actions
To make our humanitarian work self-sufficient and sustainable, we have launched a project to create a pig farm, the proceeds of which will be used to fund food distribution, the purchase of medicines, and other solidarity initiatives led by Hope With Bitcoin.
This project aims to generate regular income while having a tangible local impact:
-
🥣 Continuously support food and health aid
-
👷♂️ Create jobs for young people and unemployed people
-
♻️ Reinvest profits in other humanitarian projects
To kick-start this project, we've established a detailed budget estimate that includes the purchase of piglets, pen construction, feed, veterinary care, and management fees. 👉 Estimated cost: approximately 5,525,200 Satoshi
More details on the budget here: https://primal.net/e/nevent1qqsfmrafup9dma3wvgeqgasydjhy06rhkn8d268txmztp60533mp3xg0vuk5a
🐓 Towards a united and evolving ecosystem
Ultimately, we aim to diversify our business into chicken and goat farming and develop micro-agricultural projects. The goal is to build a resilient, local, and 100% Bitcoin-funded ecosystem that serves the most vulnerable.
💛 You can support this project now on Geyser:
https://geyser.fund/project/hopewithbitcoin/goals/552
🌍 Expansion of the area of action
We want to reach:
- More regions
- More beneficiaries
- More businesses willing to accept Bitcoin
⚫ Why Bitcoin?
The choice of Bitcoin is not ideological. It is practical, thoughtful, and strategic.
Here's why we made this choice:
- ✅ Fast and low-cost transactions
- ✅ No geographical or banking barriers
- ✅ Immutability of donations: funds cannot be diverted
- ✅ Complete traceability thanks to blockchain
- ✅ Financial education for recipients
In short, Bitcoin allows us to rebuild trust in donations and make acts of solidarity visible.
🟢 How to support us?
You can be part of the change. Here's how:
- 🤝 Donate in Bitcoin (https://geyser.fund/project/hopewithbitcoin)
- 📢 Share our posts to help us gain visibility
- 🧠 Recommend us to a partner, company, or influencer
- 💬 Join the community on Twitter, Nostr, or subscribe to Geyser to stay informed and actively participate.
Even a simple retweet can make a difference. Because every Satoshi counts.
Hope With Bitcoin is a declaration of love to humanity. It's a belief that technology can serve the heart. It's a demonstration that Bitcoin can nourish, not just enrich.
We are not an NGO, we are not a company. We are a movement, an initiative, a momentum. And this is just the beginning.
“With a little Bitcoin and a lot of love, we can change lives.”
🔗 Join us now : https://linktr.ee/hopewithbtc
-
 @ 502ab02a:a2860397
2025-05-16 01:57:09
@ 502ab02a:a2860397
2025-05-16 01:57:09หลังจากที่เราคุยกันไปแล้วเกี่ยวกับ milk 2.0 ว่ามี Perfect Day ที่เป็นหัวหาดด้านเวย์ที่ไม่มีวัว แล้วเราก็มี Formo หัวหาดด้านชีสที่ไม่มีวัว ซึ่ง 2 เจ้านี้ต่างมีสิ่งที่แต่ละคนขาดอยู่ นั่นคือ เจ้านึงขาดเคย์ซีนเด็ดๆ อีกเจ้าไม่ได้มีเวย์ที่เจ๋งพอ และแน่นอนครับ ทุกปัญหาย่อมมีธุรกิจเกิดขึ้นมาเพื่อแก้ปัญหา
วันนี้เราจะมาพบกับอีกผู้เล่นนึง ที่แก้ปัญหาทั้งหมดด้วยการ สร้างสิ่งที่ขาดขึ้นมาใหม่ ตามคาแรคเตอร์ของ "มังกรจีน" ใช่ครับ เราเคยคิดว่าโลกเทคโนโลยีมีแต่ฝรั่งเป็นเจ้าสำนัก แต่ตอนนี้ทุกมุมโลกต่างแย่งชิงอนาคตกันหมด ไม่มีใคร slow life อีกต่อไปแล้ว
เพราะในโลกที่นมไม่ใช่นม ชีสไม่ใช่ชีส และวัวไม่จำเป็นต้องกินหญ้า เรากำลังเข้าสู่ยุคที่ “นม 2.0” กำลังถูกออกแบบใหม่… ด้วยจุลินทรีย์ บริษัทหนึ่งจากจีนชื่อว่า Changing Biotech กำลังจะทำให้มันกลายเป็นความจริง ด้วยเป้าหมายที่ไม่ธรรมดา เปลี่ยนโครงสร้างนมทั้งระบบ โดยไม่ต้องใช้วัวแม้แต่ตัวเดียวเช่นกันครับ
หลายคนอาจคุ้นชื่อ Perfect Day บริษัทอเมริกันที่เป็นรายแรก ๆ ในโลกที่สามารถผลิตเวย์โปรตีนจากเชื้อราแบบไม่ใช้สัตว์ ด้วยเทคโนโลยี precision fermentation ซึ่งตอนนี้มีแบรนด์ไอศกรีม เนย และโยเกิร์ตของตัวเองกระจายขายในห้างทั่วอเมริกา แต่ Changing Biotech กลับเลือกเดินอีกเส้นทาง เส้นทางที่อาจลึกกว่า แยบยลกว่า และอาจ “กลืน” ตลาดในเอเชียโดยที่ผู้บริโภคไม่รู้ตัว
แน่นอนว่าสิทธิบัตรการค้นคว้าต่างๆมีมูลค่าสูง เบื้องหลังเทคโนโลยีของ Changing Biotech ไม่ใช่แค่การเลียนแบบ แต่คือการ สร้างใหม่ตั้งแต่ระดับจุลินทรีย์ พวกเขาไม่ได้แค่ยืมเชื้อราสำเร็จรูปอย่าง Trichoderma มาใส่ยีนโปรตีน แต่ “เพาะสายพันธุ์จุลินทรีย์ขึ้นมาเอง” เพื่อควบคุมการผลิตโปรตีนอย่างมีประสิทธิภาพ ทั้งเวย์และเคซีน ซึ่งเป็นสององค์ประกอบหลักของนมแท้ นี่คือสิ่งที่แม้แต่ Perfect Day เองก็ยังไม่ได้โฟกัสเต็มตัว เพราะยังผลิตแต่เวย์เพียงอย่างเดียว Perfect Day ใช้ Trichoderma reesei เชื้อราชนิดที่วงการอาหารใช้กันมานานในการหมักเวย์โปรตีน เชื้อราชนิดนี้ปลอดภัย และได้รับการอนุมัติให้ใช้ในอาหารในหลายประเทศ แต่ Changing Biotechกลับล้ำไปอีกขั้น พวกเขาไม่ได้ยืมของใครมาใช้ แต่ 'สร้างจุลินทรีย์แพลตฟอร์มของตัวเอง' (customized microbial chassis) และมี ความสามารถด้าน strain engineering แบบ in-house ซึ่งทำให้พวกเขาควบคุมประสิทธิภาพการผลิต และลดต้นทุนได้แบบลึกสุดใจไม่ต้องซื้อให้เปลืองครับ
การผลิตเคซีนได้ในระดับอุตสาหกรรมหมายถึงอะไร? มันหมายถึง ชีสที่ยืดได้จริง หลอมได้จริง และ “เนื้อสัมผัสแบบชีสแท้” ที่แบรนด์ plant-based ยังเลียนแบบไม่ได้ และนั่นคือกุญแจสำคัญที่ทำให้ Changing Biotech ถูกจับตามองในวงการ alt-dairy ว่าอาจเป็น “Formo เวอร์ชันจีน” ที่จะครองตลาดชีสทั้งเอเชีย Changing Biotech ตั้งเป้าผลิต ทั้งเวย์และเคซีน ซึ่งทำให้สามารถพัฒนาผลิตภัณฑ์ที่มี “เนื้อสัมผัสและการหลอมตัวแบบชีสแท้จริง” ได้ครบวงจรกว่า โดยเฉพาะพวก mozzarella และ cheddar ที่ต้องพึ่งเคซีนในการขึ้นรูป จุดนี้คือกุญแจสำคัญในการตีตลาด “ชีสพรีเมียม” ที่วัตถุดิบจากพืชทำไม่ได้
แต่ที่น่าจับตายิ่งกว่านั้นคือ ทุนและเครือข่ายในประเทศ ที่ Perfect Day ไม่มี แม้ฝั่งอเมริกาจะมีเงินลงทุนหลักเกิน 800 ล้านดอลลาร์ แต่ฐานการผลิตอยู่ในสหรัฐฯ ซึ่งทำให้มีต้นทุนสูงกว่า ส่วนในจีน Changing Biotech ได้รับแรงหนุนจากรัฐบาลจีนผ่านนโยบายสนับสนุน “เทคโนโลยีอาหารแห่งอนาคต” และมีแนวโน้มว่าจะได้สิทธิพิเศษด้าน supply chain และการผลิตระดับอุตสาหกรรมภายในประเทศจีน ซึ่งเป็น ตลาดที่ Perfect Day เจาะยาก รวมถึงได้รับแรงหนุนจากกองทุนอาหารแห่งอนาคตอย่าง Bits x Bites ที่ทำงานร่วมกับรัฐบาลจีนโดยตรงในแผน 5 ปีด้านเทคโนโลยีอาหาร เป้าหมายชัดเจน ลดการพึ่งพาโปรตีนจากสัตว์ และสร้างระบบนมแห่งชาติแบบไร้สัตว์
โมเดลของพวกเขาต่างกับ Perfect Day ที่เน้นการสร้างแบรนด์ (เช่น Brave Robot, Modern Kitchen) และขายตรงกับผู้บริโภค แต่ Changing Biotech ไม่ใช่การตั้งแบรนด์ขายแข่งกันในห้าง แต่เป็น “ผู้อยู่เบื้องหลัง” ของแบรนด์ใหญ่อื่น ๆ โดยซัพพลายโปรตีนให้แบบ OEM ให้กับผู้ผลิตอาหารในจีน ซึ่งทำให้สามารถฝังตัวเข้า supply chain ของอุตสาหกรรมนมจีนได้เงียบ ๆ แต่ทรงพลัง โมเดลนี้คล้ายกับ Givaudan หรือ DSM ที่เน้นการเป็นผู้อยู่เบื้องหลังผลิตภัณฑ์แบรนด์อื่น
จะเรียกว่า Perfect Day คือ Apple ของนมไร้สัตว์ก็ได้ แต่ Changing Biotech กำลังเป็น Huawei ของอุตสาหกรรมนม ที่สร้างเทคโนโลยีขึ้นเองทั้งระบบ ควบคุมเบ็ดเสร็จตั้งแต่เชื้อจุลินทรีย์ยันขั้นตอนผลิต แล้วส่งต่อให้แบรนด์อื่นใช้แบบครบวงจร
ในวันที่ผู้บริโภคในจีนตักไอศกรีม “จากครีมจุลินทรีย์” หรือกินชีส “ไม่มีสัตว์เจือปน” อาจไม่มีใครรู้เลยว่าเบื้องหลังของรสสัมผัสนั้น คือจุลินทรีย์จากโรงงานที่พัฒนาโดย Changing Biotech ทั้งสิ้น
คำถามคือ แล้วมันดีต่อสุขภาพแค่ไหน? มันดีกว่าการรีดนมจากวัวจริง ๆ หรือแค่ดีต่อ narrative ของคนเมืองที่อยาก feel good แค่นั้น?
แล้วถ้าทุกประเทศเดินตามเทรนด์นี้ ใครกันแน่จะเป็นเจ้าของ “สูตรโปรตีนแห่งอนาคต” ที่ครองอำนาจอาหารของทั้งโลก?
คำตอบอาจไม่ได้อยู่ในกล่องนม แต่ในห้องแล็บจุลินทรีย์ของบริษัทที่เราไม่เคยได้ยินชื่อ
ยิ่งเราคุยกันนานเท่าไร ยิ่งรู้สึกแล้วใช่ไหมครับว่า อาหารอนาคต ไม่ใช่อาหารที่จะเกิดขึ้นในอนาคต แต่เป็น อาหารที่เราจะถูกครอบงำในอนาคต ซึ่งเริ่มไปแล้ว . . . วันนี้
นึกภาพวันที่ทุกคนล้วนรังเกียจนมจากวัว แล้วยินดีโอบกอดรับนมจากจุลินทรีย์ ด้วยความยินดีปรีดา
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 5490af12:d4710677
2025-05-16 00:28:35
@ 5490af12:d4710677
2025-05-16 00:28:35| | | ------------------------------------------------------------------------- | | bitcoinmetronome.com | | cornjoin.com | | decentralisedvalueexchange.com | | decentralizedvalueexchange.com | | memeswaps.com | | bitcoinculture.org |
-
 @ eac63075:b4988b48
2025-01-04 19:41:34
@ eac63075:b4988b48
2025-01-04 19:41:34Since its creation in 2009, Bitcoin has symbolized innovation and resilience. However, from time to time, alarmist narratives arise about emerging technologies that could "break" its security. Among these, quantum computing stands out as one of the most recurrent. But does quantum computing truly threaten Bitcoin? And more importantly, what is the community doing to ensure the protocol remains invulnerable?
The answer, contrary to sensationalist headlines, is reassuring: Bitcoin is secure, and the community is already preparing for a future where quantum computing becomes a practical reality. Let’s dive into this topic to understand why the concerns are exaggerated and how the development of BIP-360 demonstrates that Bitcoin is one step ahead.
What Is Quantum Computing, and Why Is Bitcoin Not Threatened?
Quantum computing leverages principles of quantum mechanics to perform calculations that, in theory, could exponentially surpass classical computers—and it has nothing to do with what so-called “quantum coaches” teach to scam the uninformed. One of the concerns is that this technology could compromise two key aspects of Bitcoin’s security:
- Wallets: These use elliptic curve algorithms (ECDSA) to protect private keys. A sufficiently powerful quantum computer could deduce a private key from its public key.
- Mining: This is based on the SHA-256 algorithm, which secures the consensus process. A quantum attack could, in theory, compromise the proof-of-work mechanism.
Understanding Quantum Computing’s Attack Priorities
While quantum computing is often presented as a threat to Bitcoin, not all parts of the network are equally vulnerable. Theoretical attacks would be prioritized based on two main factors: ease of execution and potential reward. This creates two categories of attacks:
1. Attacks on Wallets
Bitcoin wallets, secured by elliptic curve algorithms, would be the initial targets due to the relative vulnerability of their public keys, especially those already exposed on the blockchain. Two attack scenarios stand out:
-
Short-term attacks: These occur during the interval between sending a transaction and its inclusion in a block (approximately 10 minutes). A quantum computer could intercept the exposed public key and derive the corresponding private key to redirect funds by creating a transaction with higher fees.
-
Long-term attacks: These focus on old wallets whose public keys are permanently exposed. Wallets associated with Satoshi Nakamoto, for example, are especially vulnerable because they were created before the practice of using hashes to mask public keys.
We can infer a priority order for how such attacks might occur based on urgency and importance.
 Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)
Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)2. Attacks on Mining
Targeting the SHA-256 algorithm, which secures the mining process, would be the next objective. However, this is far more complex and requires a level of quantum computational power that is currently non-existent and far from realization. A successful attack would allow for the recalculation of all possible hashes to dominate the consensus process and potentially "mine" it instantly.
 Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin Attacks
Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin AttacksRecently, Narcelio asked me about a statement I made on Tubacast:
https://x.com/eddieoz/status/1868371296683511969
If an attack became a reality before Bitcoin was prepared, it would be necessary to define the last block prior to the attack and proceed from there using a new hashing algorithm. The solution would resemble the response to the infamous 2013 bug. It’s a fact that this would cause market panic, and Bitcoin's price would drop significantly, creating a potential opportunity for the well-informed.
Preferably, if developers could anticipate the threat and had time to work on a solution and build consensus before an attack, they would simply decide on a future block for the fork, which would then adopt the new algorithm. It might even rehash previous blocks (reaching consensus on them) to avoid potential reorganization through the re-mining of blocks using the old hash. (I often use the term "shielding" old transactions).
How Can Users Protect Themselves?
While quantum computing is still far from being a practical threat, some simple measures can already protect users against hypothetical scenarios:
- Avoid using exposed public keys: Ensure funds sent to old wallets are transferred to new ones that use public key hashes. This reduces the risk of long-term attacks.
- Use modern wallets: Opt for wallets compatible with SegWit or Taproot, which implement better security practices.
- Monitor security updates: Stay informed about updates from the Bitcoin community, such as the implementation of BIP-360, which will introduce quantum-resistant addresses.
- Do not reuse addresses: Every transaction should be associated with a new address to minimize the risk of repeated exposure of the same public key.
- Adopt secure backup practices: Create offline backups of private keys and seeds in secure locations, protected from unauthorized access.
BIP-360 and Bitcoin’s Preparation for the Future
Even though quantum computing is still beyond practical reach, the Bitcoin community is not standing still. A concrete example is BIP-360, a proposal that establishes the technical framework to make wallets resistant to quantum attacks.
BIP-360 addresses three main pillars:
- Introduction of quantum-resistant addresses: A new address format starting with "BC1R" will be used. These addresses will be compatible with post-quantum algorithms, ensuring that stored funds are protected from future attacks.
- Compatibility with the current ecosystem: The proposal allows users to transfer funds from old addresses to new ones without requiring drastic changes to the network infrastructure.
- Flexibility for future updates: BIP-360 does not limit the choice of specific algorithms. Instead, it serves as a foundation for implementing new post-quantum algorithms as technology evolves.
This proposal demonstrates how Bitcoin can adapt to emerging threats without compromising its decentralized structure.
Post-Quantum Algorithms: The Future of Bitcoin Cryptography
The community is exploring various algorithms to protect Bitcoin from quantum attacks. Among the most discussed are:
- Falcon: A solution combining smaller public keys with compact digital signatures. Although it has been tested in limited scenarios, it still faces scalability and performance challenges.
- Sphincs: Hash-based, this algorithm is renowned for its resilience, but its signatures can be extremely large, making it less efficient for networks like Bitcoin’s blockchain.
- Lamport: Created in 1977, it’s considered one of the earliest post-quantum security solutions. Despite its reliability, its gigantic public keys (16,000 bytes) make it impractical and costly for Bitcoin.
Two technologies show great promise and are well-regarded by the community:
- Lattice-Based Cryptography: Considered one of the most promising, it uses complex mathematical structures to create systems nearly immune to quantum computing. Its implementation is still in its early stages, but the community is optimistic.
- Supersingular Elliptic Curve Isogeny: These are very recent digital signature algorithms and require extensive study and testing before being ready for practical market use.
The final choice of algorithm will depend on factors such as efficiency, cost, and integration capability with the current system. Additionally, it is preferable that these algorithms are standardized before implementation, a process that may take up to 10 years.
Why Quantum Computing Is Far from Being a Threat
The alarmist narrative about quantum computing overlooks the technical and practical challenges that still need to be overcome. Among them:
- Insufficient number of qubits: Current quantum computers have only a few hundred qubits, whereas successful attacks would require millions.
- High error rate: Quantum stability remains a barrier to reliable large-scale operations.
- High costs: Building and operating large-scale quantum computers requires massive investments, limiting their use to scientific or specific applications.
Moreover, even if quantum computers make significant advancements, Bitcoin is already adapting to ensure its infrastructure is prepared to respond.
Conclusion: Bitcoin’s Secure Future
Despite advancements in quantum computing, the reality is that Bitcoin is far from being threatened. Its security is ensured not only by its robust architecture but also by the community’s constant efforts to anticipate and mitigate challenges.
The implementation of BIP-360 and the pursuit of post-quantum algorithms demonstrate that Bitcoin is not only resilient but also proactive. By adopting practical measures, such as using modern wallets and migrating to quantum-resistant addresses, users can further protect themselves against potential threats.
Bitcoin’s future is not at risk—it is being carefully shaped to withstand any emerging technology, including quantum computing.
-
 @ eac63075:b4988b48
2024-11-09 17:57:27
@ eac63075:b4988b48
2024-11-09 17:57:27Based on a recent paper that included collaboration from renowned experts such as Lynn Alden, Steve Lee, and Ren Crypto Fish, we discuss in depth how Bitcoin's consensus is built, the main risks, and the complex dynamics of protocol upgrades.
Podcast https://www.fountain.fm/episode/wbjD6ntQuvX5u2G5BccC
Presentation https://gamma.app/docs/Analyzing-Bitcoin-Consensus-Risks-in-Protocol-Upgrades-p66axxjwaa37ksn
1. Introduction to Consensus in Bitcoin
Consensus in Bitcoin is the foundation that keeps the network secure and functional, allowing users worldwide to perform transactions in a decentralized manner without the need for intermediaries. Since its launch in 2009, Bitcoin is often described as an "immutable" system designed to resist changes, and it is precisely this resistance that ensures its security and stability.
The central idea behind consensus in Bitcoin is to create a set of acceptance rules for blocks and transactions, ensuring that all network participants agree on the transaction history. This prevents "double-spending," where the same bitcoin could be used in two simultaneous transactions, something that would compromise trust in the network.
Evolution of Consensus in Bitcoin
Over the years, consensus in Bitcoin has undergone several adaptations, and the way participants agree on changes remains a delicate process. Unlike traditional systems, where changes can be imposed from the top down, Bitcoin operates in a decentralized model where any significant change needs the support of various groups of stakeholders, including miners, developers, users, and large node operators.
Moreover, the update process is extremely cautious, as hasty changes can compromise the network's security. As a result, the philosophy of "don't fix what isn't broken" prevails, with improvements happening incrementally and only after broad consensus among those involved. This model can make progress seem slow but ensures that Bitcoin remains faithful to the principles of security and decentralization.
2. Technical Components of Consensus
Bitcoin's consensus is supported by a set of technical rules that determine what is considered a valid transaction and a valid block on the network. These technical aspects ensure that all nodes—the computers that participate in the Bitcoin network—agree on the current state of the blockchain. Below are the main technical components that form the basis of the consensus.
Validation of Blocks and Transactions
The validation of blocks and transactions is the central point of consensus in Bitcoin. A block is only considered valid if it meets certain criteria, such as maximum size, transaction structure, and the solving of the "Proof of Work" problem. The proof of work, required for a block to be included in the blockchain, is a computational process that ensures the block contains significant computational effort—protecting the network against manipulation attempts.
Transactions, in turn, need to follow specific input and output rules. Each transaction includes cryptographic signatures that prove the ownership of the bitcoins sent, as well as validation scripts that verify if the transaction conditions are met. This validation system is essential for network nodes to autonomously confirm that each transaction follows the rules.
Chain Selection
Another fundamental technical issue for Bitcoin's consensus is chain selection, which becomes especially important in cases where multiple versions of the blockchain coexist, such as after a network split (fork). To decide which chain is the "true" one and should be followed, the network adopts the criterion of the highest accumulated proof of work. In other words, the chain with the highest number of valid blocks, built with the greatest computational effort, is chosen by the network as the official one.
This criterion avoids permanent splits because it encourages all nodes to follow the same main chain, reinforcing consensus.
Soft Forks vs. Hard Forks
In the consensus process, protocol changes can happen in two ways: through soft forks or hard forks. These variations affect not only the protocol update but also the implications for network users:
-
Soft Forks: These are changes that are backward compatible. Only nodes that adopt the new update will follow the new rules, but old nodes will still recognize the blocks produced with these rules as valid. This compatibility makes soft forks a safer option for updates, as it minimizes the risk of network division.
-
Hard Forks: These are updates that are not backward compatible, requiring all nodes to update to the new version or risk being separated from the main chain. Hard forks can result in the creation of a new coin, as occurred with the split between Bitcoin and Bitcoin Cash in 2017. While hard forks allow for deeper changes, they also bring significant risks of network fragmentation.
These technical components form the base of Bitcoin's security and resilience, allowing the system to remain functional and immutable without losing the necessary flexibility to evolve over time.
3. Stakeholders in Bitcoin's Consensus
Consensus in Bitcoin is not decided centrally. On the contrary, it depends on the interaction between different groups of stakeholders, each with their motivations, interests, and levels of influence. These groups play fundamental roles in how changes are implemented or rejected on the network. Below, we explore the six main stakeholders in Bitcoin's consensus.
1. Economic Nodes
Economic nodes, usually operated by exchanges, custody providers, and large companies that accept Bitcoin, exert significant influence over consensus. Because they handle large volumes of transactions and act as a connection point between the Bitcoin ecosystem and the traditional financial system, these nodes have the power to validate or reject blocks and to define which version of the software to follow in case of a fork.
Their influence is proportional to the volume of transactions they handle, and they can directly affect which chain will be seen as the main one. Their incentive is to maintain the network's stability and security to preserve its functionality and meet regulatory requirements.
2. Investors
Investors, including large institutional funds and individual Bitcoin holders, influence consensus indirectly through their impact on the asset's price. Their buying and selling actions can affect Bitcoin's value, which in turn influences the motivation of miners and other stakeholders to continue investing in the network's security and development.
Some institutional investors have agreements with custodians that may limit their ability to act in network split situations. Thus, the impact of each investor on consensus can vary based on their ownership structure and how quickly they can react to a network change.
3. Media Influencers
Media influencers, including journalists, analysts, and popular personalities on social media, have a powerful role in shaping public opinion about Bitcoin and possible updates. These influencers can help educate the public, promote debates, and bring transparency to the consensus process.
On the other hand, the impact of influencers can be double-edged: while they can clarify complex topics, they can also distort perceptions by amplifying or minimizing change proposals. This makes them a force both of support and resistance to consensus.
4. Miners
Miners are responsible for validating transactions and including blocks in the blockchain. Through computational power (hashrate), they also exert significant influence over consensus decisions. In update processes, miners often signal their support for a proposal, indicating that the new version is safe to use. However, this signaling is not always definitive, and miners can change their position if they deem it necessary.
Their incentive is to maximize returns from block rewards and transaction fees, as well as to maintain the value of investments in their specialized equipment, which are only profitable if the network remains stable.
5. Protocol Developers
Protocol developers, often called "Core Developers," are responsible for writing and maintaining Bitcoin's code. Although they do not have direct power over consensus, they possess an informal veto power since they decide which changes are included in the main client (Bitcoin Core). This group also serves as an important source of technical knowledge, helping guide decisions and inform other stakeholders.
Their incentive lies in the continuous improvement of the network, ensuring security and decentralization. Many developers are funded by grants and sponsorships, but their motivations generally include a strong ideological commitment to Bitcoin's principles.
6. Users and Application Developers
This group includes people who use Bitcoin in their daily transactions and developers who build solutions based on the network, such as wallets, exchanges, and payment platforms. Although their power in consensus is less than that of miners or economic nodes, they play an important role because they are responsible for popularizing Bitcoin's use and expanding the ecosystem.
If application developers decide not to adopt an update, this can affect compatibility and widespread acceptance. Thus, they indirectly influence consensus by deciding which version of the protocol to follow in their applications.
These stakeholders are vital to the consensus process, and each group exerts influence according to their involvement, incentives, and ability to act in situations of change. Understanding the role of each makes it clearer how consensus is formed and why it is so difficult to make significant changes to Bitcoin.
4. Mechanisms for Activating Updates in Bitcoin
For Bitcoin to evolve without compromising security and consensus, different mechanisms for activating updates have been developed over the years. These mechanisms help coordinate changes among network nodes to minimize the risk of fragmentation and ensure that updates are implemented in an orderly manner. Here, we explore some of the main methods used in Bitcoin, their advantages and disadvantages, as well as historical examples of significant updates.
Flag Day
The Flag Day mechanism is one of the simplest forms of activating changes. In it, a specific date or block is determined as the activation moment, and all nodes must be updated by that point. This method does not involve prior signaling; participants simply need to update to the new software version by the established day or block.
-
Advantages: Simplicity and predictability are the main benefits of Flag Day, as everyone knows the exact activation date.
-
Disadvantages: Inflexibility can be a problem because there is no way to adjust the schedule if a significant part of the network has not updated. This can result in network splits if a significant number of nodes are not ready for the update.
An example of Flag Day was the Pay to Script Hash (P2SH) update in 2012, which required all nodes to adopt the change to avoid compatibility issues.
BIP34 and BIP9
BIP34 introduced a more dynamic process, in which miners increase the version number in block headers to signal the update. When a predetermined percentage of the last blocks is mined with this new version, the update is automatically activated. This model later evolved with BIP9, which allowed multiple updates to be signaled simultaneously through "version bits," each corresponding to a specific change.
-
Advantages: Allows the network to activate updates gradually, giving more time for participants to adapt.
-
Disadvantages: These methods rely heavily on miner support, which means that if a sufficient number of miners do not signal the update, it can be delayed or not implemented.
BIP9 was used in the activation of SegWit (BIP141) but faced challenges because some miners did not signal their intent to activate, leading to the development of new mechanisms.
User Activated Soft Forks (UASF) and User Resisted Soft Forks (URSF)
To increase the decision-making power of ordinary users, the concept of User Activated Soft Fork (UASF) was introduced, allowing node operators, not just miners, to determine consensus for a change. In this model, nodes set a date to start rejecting blocks that are not in compliance with the new update, forcing miners to adapt or risk having their blocks rejected by the network.
URSF, in turn, is a model where nodes reject blocks that attempt to adopt a specific update, functioning as resistance against proposed changes.
-
Advantages: UASF returns decision-making power to node operators, ensuring that changes do not depend solely on miners.
-
Disadvantages: Both UASF and URSF can generate network splits, especially in cases of strong opposition among different stakeholders.
An example of UASF was the activation of SegWit in 2017, where users supported activation independently of miner signaling, which ended up forcing its adoption.
BIP8 (LOT=True)
BIP8 is an evolution of BIP9, designed to prevent miners from indefinitely blocking a change desired by the majority of users and developers. BIP8 allows setting a parameter called "lockinontimeout" (LOT) as true, which means that if the update has not been fully signaled by a certain point, it is automatically activated.
-
Advantages: Ensures that changes with broad support among users are not blocked by miners who wish to maintain the status quo.
-
Disadvantages: Can lead to network splits if miners or other important stakeholders do not support the update.
Although BIP8 with LOT=True has not yet been used in Bitcoin, it is a proposal that can be applied in future updates if necessary.
These activation mechanisms have been essential for Bitcoin's development, allowing updates that keep the network secure and functional. Each method brings its own advantages and challenges, but all share the goal of preserving consensus and network cohesion.
5. Risks and Considerations in Consensus Updates
Consensus updates in Bitcoin are complex processes that involve not only technical aspects but also political, economic, and social considerations. Due to the network's decentralized nature, each change brings with it a set of risks that need to be carefully assessed. Below, we explore some of the main challenges and future scenarios, as well as the possible impacts on stakeholders.
Network Fragility with Alternative Implementations
One of the main risks associated with consensus updates is the possibility of network fragmentation when there are alternative software implementations. If an update is implemented by a significant group of nodes but rejected by others, a network split (fork) can occur. This creates two competing chains, each with a different version of the transaction history, leading to unpredictable consequences for users and investors.
Such fragmentation weakens Bitcoin because, by dividing hashing power (computing) and coin value, it reduces network security and investor confidence. A notable example of this risk was the fork that gave rise to Bitcoin Cash in 2017 when disagreements over block size resulted in a new chain and a new asset.
Chain Splits and Impact on Stakeholders
Chain splits are a significant risk in update processes, especially in hard forks. During a hard fork, the network is split into two separate chains, each with its own set of rules. This results in the creation of a new coin and leaves users with duplicated assets on both chains. While this may seem advantageous, in the long run, these splits weaken the network and create uncertainties for investors.
Each group of stakeholders reacts differently to a chain split:
-
Institutional Investors and ETFs: Face regulatory and compliance challenges because many of these assets are managed under strict regulations. The creation of a new coin requires decisions to be made quickly to avoid potential losses, which may be hampered by regulatory constraints.
-
Miners: May be incentivized to shift their computing power to the chain that offers higher profitability, which can weaken one of the networks.
-
Economic Nodes: Such as major exchanges and custody providers, have to quickly choose which chain to support, influencing the perceived value of each network.
Such divisions can generate uncertainties and loss of value, especially for institutional investors and those who use Bitcoin as a store of value.
Regulatory Impacts and Institutional Investors
With the growing presence of institutional investors in Bitcoin, consensus changes face new compliance challenges. Bitcoin ETFs, for example, are required to follow strict rules about which assets they can include and how chain split events should be handled. The creation of a new asset or migration to a new chain can complicate these processes, creating pressure for large financial players to quickly choose a chain, affecting the stability of consensus.
Moreover, decisions regarding forks can influence the Bitcoin futures and derivatives market, affecting perception and adoption by new investors. Therefore, the need to avoid splits and maintain cohesion is crucial to attract and preserve the confidence of these investors.
Security Considerations in Soft Forks and Hard Forks
While soft forks are generally preferred in Bitcoin for their backward compatibility, they are not without risks. Soft forks can create different classes of nodes on the network (updated and non-updated), which increases operational complexity and can ultimately weaken consensus cohesion. In a network scenario with fragmentation of node classes, Bitcoin's security can be affected, as some nodes may lose part of the visibility over updated transactions or rules.
In hard forks, the security risk is even more evident because all nodes need to adopt the new update to avoid network division. Experience shows that abrupt changes can create temporary vulnerabilities, in which malicious agents try to exploit the transition to attack the network.
Bounty Claim Risks and Attack Scenarios
Another risk in consensus updates are so-called "bounty claims"—accumulated rewards that can be obtained if an attacker manages to split or deceive a part of the network. In a conflict scenario, a group of miners or nodes could be incentivized to support a new update or create an alternative version of the software to benefit from these rewards.
These risks require stakeholders to carefully assess each update and the potential vulnerabilities it may introduce. The possibility of "bounty claims" adds a layer of complexity to consensus because each interest group may see a financial opportunity in a change that, in the long term, may harm network stability.
The risks discussed above show the complexity of consensus in Bitcoin and the importance of approaching it gradually and deliberately. Updates need to consider not only technical aspects but also economic and social implications, in order to preserve Bitcoin's integrity and maintain trust among stakeholders.
6. Recommendations for the Consensus Process in Bitcoin
To ensure that protocol changes in Bitcoin are implemented safely and with broad support, it is essential that all stakeholders adopt a careful and coordinated approach. Here are strategic recommendations for evaluating, supporting, or rejecting consensus updates, considering the risks and challenges discussed earlier, along with best practices for successful implementation.
1. Careful Evaluation of Proposal Maturity
Stakeholders should rigorously assess the maturity level of a proposal before supporting its implementation. Updates that are still experimental or lack a robust technical foundation can expose the network to unnecessary risks. Ideally, change proposals should go through an extensive testing phase, have security audits, and receive review and feedback from various developers and experts.
2. Extensive Testing in Secure and Compatible Networks
Before an update is activated on the mainnet, it is essential to test it on networks like testnet and signet, and whenever possible, on other compatible networks that offer a safe and controlled environment to identify potential issues. Testing on networks like Litecoin was fundamental for the safe launch of innovations like SegWit and the Lightning Network, allowing functionalities to be validated on a lower-impact network before being implemented on Bitcoin.
The Liquid Network, developed by Blockstream, also plays an important role as an experimental network for new proposals, such as OP_CAT. By adopting these testing environments, stakeholders can mitigate risks and ensure that the update is reliable and secure before being adopted by the main network.
3. Importance of Stakeholder Engagement
The success of a consensus update strongly depends on the active participation of all stakeholders. This includes economic nodes, miners, protocol developers, investors, and end users. Lack of participation can lead to inadequate decisions or even future network splits, which would compromise Bitcoin's security and stability.
4. Key Questions for Evaluating Consensus Proposals
To assist in decision-making, each group of stakeholders should consider some key questions before supporting a consensus change:
- Does the proposal offer tangible benefits for Bitcoin's security, scalability, or usability?
- Does it maintain backward compatibility or introduce the risk of network split?
- Are the implementation requirements clear and feasible for each group involved?
- Are there clear and aligned incentives for all stakeholder groups to accept the change?
5. Coordination and Timing in Implementations
Timing is crucial. Updates with short activation windows can force a split because not all nodes and miners can update simultaneously. Changes should be planned with ample deadlines to allow all stakeholders to adjust their systems, avoiding surprises that could lead to fragmentation.
Mechanisms like soft forks are generally preferable to hard forks because they allow a smoother transition. Opting for backward-compatible updates when possible facilitates the process and ensures that nodes and miners can adapt without pressure.
6. Continuous Monitoring and Re-evaluation
After an update, it's essential to monitor the network to identify problems or side effects. This continuous process helps ensure cohesion and trust among all participants, keeping Bitcoin as a secure and robust network.
These recommendations, including the use of secure networks for extensive testing, promote a collaborative and secure environment for Bitcoin's consensus process. By adopting a deliberate and strategic approach, stakeholders can preserve Bitcoin's value as a decentralized and censorship-resistant network.
7. Conclusion
Consensus in Bitcoin is more than a set of rules; it's the foundation that sustains the network as a decentralized, secure, and reliable system. Unlike centralized systems, where decisions can be made quickly, Bitcoin requires a much more deliberate and cooperative approach, where the interests of miners, economic nodes, developers, investors, and users must be considered and harmonized. This governance model may seem slow, but it is fundamental to preserving the resilience and trust that make Bitcoin a global store of value and censorship-resistant.
Consensus updates in Bitcoin must balance the need for innovation with the preservation of the network's core principles. The development process of a proposal needs to be detailed and rigorous, going through several testing stages, such as in testnet, signet, and compatible networks like Litecoin and Liquid Network. These networks offer safe environments for proposals to be analyzed and improved before being launched on the main network.
Each proposed change must be carefully evaluated regarding its maturity, impact, backward compatibility, and support among stakeholders. The recommended key questions and appropriate timing are critical to ensure that an update is adopted without compromising network cohesion. It's also essential that the implementation process is continuously monitored and re-evaluated, allowing adjustments as necessary and minimizing the risk of instability.
By following these guidelines, Bitcoin's stakeholders can ensure that the network continues to evolve safely and robustly, maintaining user trust and further solidifying its role as one of the most resilient and innovative digital assets in the world. Ultimately, consensus in Bitcoin is not just a technical issue but a reflection of its community and the values it represents: security, decentralization, and resilience.
8. Links
Whitepaper: https://github.com/bitcoin-cap/bcap
Youtube (pt-br): https://www.youtube.com/watch?v=rARycAibl9o&list=PL-qnhF0qlSPkfhorqsREuIu4UTbF0h4zb
-
-
 @ 472f440f:5669301e
2025-05-16 00:18:45
@ 472f440f:5669301e
2025-05-16 00:18:45Marty's Bent
It's been a pretty historic week for the United States as it pertains to geopolitical relations in the Middle East. President Trump and many members of his administration, including AI and Crypto Czar David Sacks and Treasury Secretary Scott Bessent, traveled across the Middle East making deals with countries like Qatar, Saudi Arabia, the United Arab Emirates, Syria, and others. Many are speculating that Iran may be included in some behind the scenes deal as well. This trip to the Middle East makes sense considering the fact that China is also vying for favorable relationships with those countries. The Middle East is a power player in the world, and it seems pretty clear that Donald Trump is dead set on ensuring that they choose the United States over China as the world moves towards a more multi-polar reality.
Many are calling the events of this week the Riyadh Accords. There were many deals that were struck in relation to artificial intelligence, defense, energy and direct investments in the United States. A truly prolific power play and demonstration of deal-making ability of Donald Trump, if you ask me. Though I will admit some of the numbers that were thrown out by some of the countries were a bit egregious. We shall see how everything plays out in the coming years. It will be interesting to see how China reacts to this power move by the United States.
While all this was going on, there was something happening back in the United States that many people outside of fringe corners of FinTwit are not talking about, which is the fact that the 10-year and 30-year U.S. Treasury bond yields are back on the rise. Yesterday, they surpassed the levels of mid-April that caused a market panic and are hovering back around levels that have not been seen since right before Donald Trump's inauguration.


I imagine that there isn't as much of an uproar right now because I'm pretty confident the media freakouts we were experiencing in mid-April were driven by the fact that many large hedge funds found themselves off sides of large levered basis trades. I wouldn't be surprised if those funds have decreased their leverage in those trades and bond yields being back to mid-April levels is not affecting those funds as much as they were last month. But the point stands, the 10-year and 30-year yields are significantly elevated with the 30-year approaching 5%. Regardless of the deals that are currently being made in the Middle East, the Treasury has a big problem on its hands. It still has to roll over many trillions worth of debt over over the next few years and doing so at these rates is going to be massively detrimental to fiscal deficits over the next decade. The interest expense on the debt is set to explode in the coming years.
On that note, data from the first quarter of 2025 has been released by the government and despite all the posturing by the Trump administration around DOGE and how tariffs are going to be beneficial for the U.S. economy, deficits are continuing to explode while the interest expense on the debt has definitively surpassed our annual defense budget.
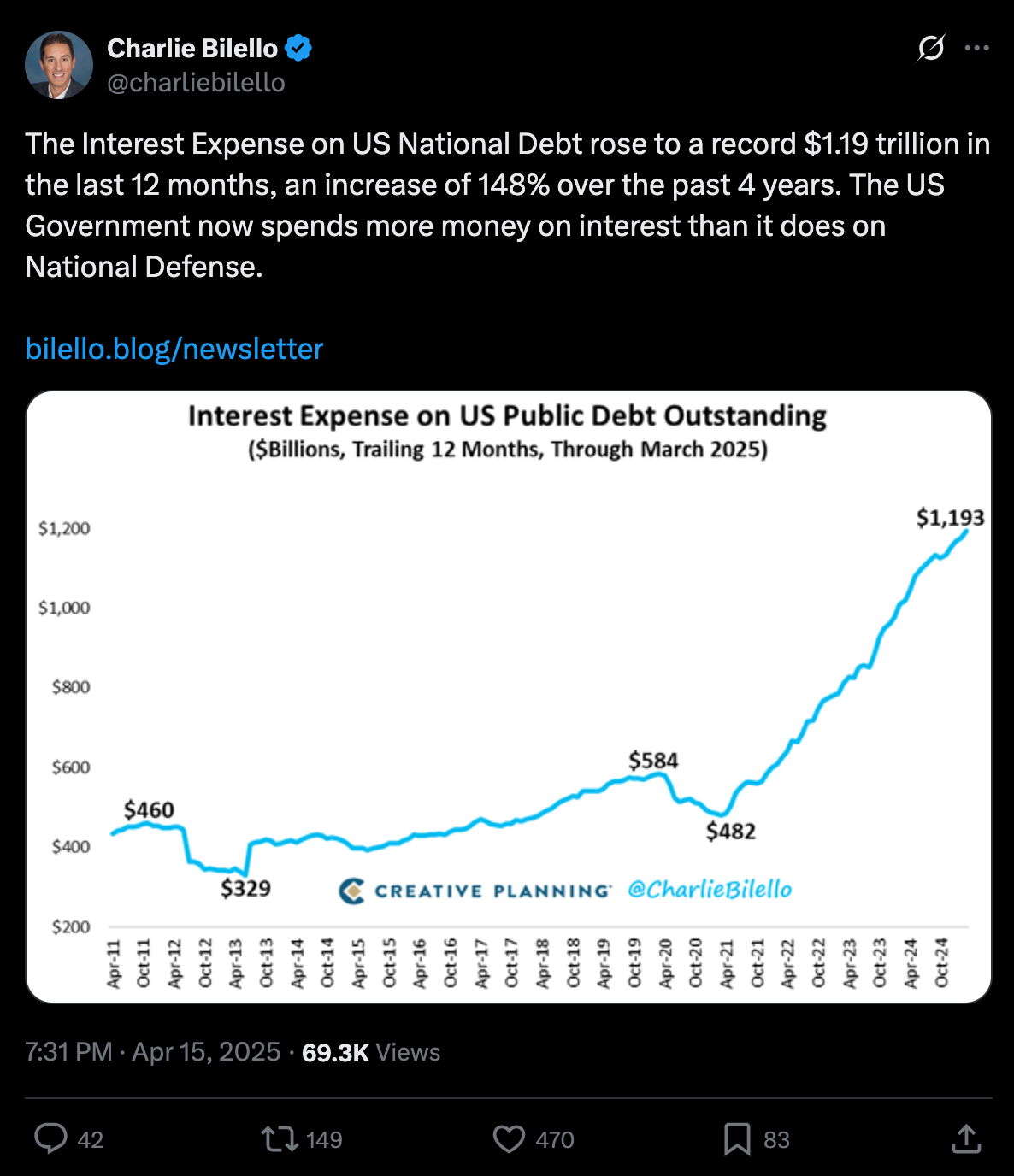
via Charlie Bilello
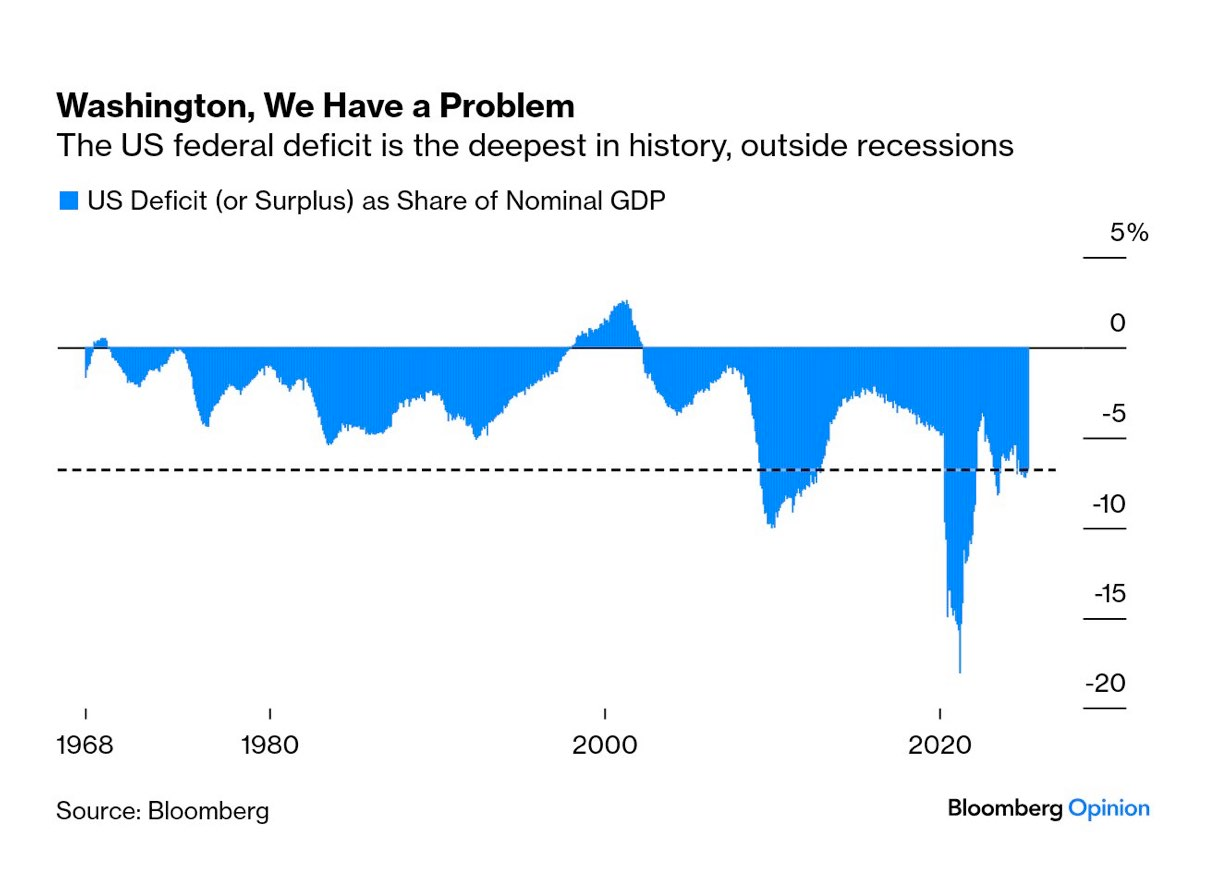
via Mohamed Al-Erian
To make matters worse, as things are deteriorating on the fiscal side of things, the U.S. consumer is getting crushed by credit. The 90-plus day delinquency rates for credit card and auto loans are screaming higher right now.

via TXMC
One has to wonder how long all this can continue without some sort of liquidity crunch. Even though equities markets have recovered from their post-Liberation Day month long bear market, I would not be surprised if what we're witnessing is a dead cat bounce that can only be continued if the money printers are turned back on. Something's got to give, both on the fiscal side and in the private markets where the Common Man is getting crushed because he's been forced to take on insane amounts of debt to stay afloat after years of elevated levels of inflation. Add on the fact that AI has reached a state of maturity that will enable companies to replace their current meat suit workers with an army of cheap, efficient and fast digital workers and it isn't hard to see that some sort of employment crisis could be on the horizon as well.
Now is not the time to get complacent. While I do believe that the deals that are currently being made in the Middle East are probably in the best interest of the United States as the world, again, moves toward a more multi-polar reality, we are facing problems that one cannot simply wish away. They will need to be confronted. And as we've seen throughout the 21st century, the problems are usually met head-on with a money printer.
I take no pleasure in saying this because it is a bit uncouth to be gleeful to benefit from the strife of others, but it is pretty clear to me that all signs are pointing to bitcoin benefiting massively from everything that is going on. The shift towards a more multi-polar world, the runaway debt situation here in the United States, the increasing deficits, the AI job replacements and the consumer credit crisis that is currently unfolding, All will need to be "solved" by turning on the money printers to levels they've never been pushed to before.
Weird times we're living in.
China's Manufacturing Dominance: Why It Matters for the U.S.
In my recent conversation with Lyn Alden, she highlighted how China has rapidly ascended the manufacturing value chain. As Lyn pointed out, China transformed from making "sneakers and plastic trinkets" to becoming the world's largest auto exporter in just four years. This dramatic shift represents more than economic success—it's a strategic power play. China now dominates solar panel production with greater market control than OPEC has over oil and maintains near-monopoly control of rare earth elements crucial for modern technology.
"China makes like 10 times more steel than the United States does... which is relevant in ship making. It's relevant in all sorts of stuff." - Lyn Alden
Perhaps most concerning, as Lyn emphasized, is China's financial leverage. They hold substantial U.S. assets that could be strategically sold to disrupt U.S. treasury market functioning. This combination of manufacturing dominance, resource control, and financial leverage gives China significant negotiating power in any trade disputes, making our attempts to reshoring manufacturing all the more challenging.
Check out the full podcast here for more on Triffin's dilemma, Bitcoin's role in monetary transition, and the energy requirements for rebuilding America's industrial base.
Headlines of the Day
Financial Times Under Fire Over MicroStrategy Bitcoin Coverage - via X
Trump in Qatar: Historic Boeing Deal Signed - via X
Get our new STACK SATS hat - via tftcmerch.io
Johnson Backs Stock Trading Ban; Passage Chances Slim - via X
Take the First Step Off the Exchange
Bitkey is an easy, secure way to move your Bitcoin into self-custody. With simple setup and built-in recovery, it’s the perfect starting point for getting your coins off centralized platforms and into cold storage—no complexity, no middlemen.
Take control. Start with Bitkey.
Use the promo code “TFTC20” during checkout for 20% off
Ten31, the largest bitcoin-focused investor, has deployed 158,469 sats | $150.00M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/invest.
Final thought...
Building things of value is satisfying.
Get this newsletter sent to your inbox daily: https://www.tftc.io/bitcoin-brief/
Subscribe to our YouTube channels and follow us on Nostr and X:
-
 @ c9badfea:610f861a
2025-05-15 23:51:35
@ c9badfea:610f861a
2025-05-15 23:51:35- Install SDAI (it's free and open source)
- Launch the app, and allow notifications when prompted
- Complete the introduction to get started
- Set Local Diffusion Microsoft ONNX as provider
- In the configuration step, Download a model (such as Real Vision) and wait for the process to finish
- Once the model is downloaded, tap on it and then select Setup
- You can now create images offline by entering a Prompt and tapping 🪄 Imagine
ℹ️ Download the tracking-free FOSS variant
ℹ️ Internet connection is only required for the initial model download
ℹ️ To speed up image generation, consider reducing the image size (e.g. 256x256)
-
 @ 28e13303:84bb7266
2025-05-15 23:37:29
@ 28e13303:84bb7266
2025-05-15 23:37:29⚠️ Disclaimer: This article is for educational purposes only. Flash USDT is a blockchain simulation tool used for wallet testing, UI development, or demonstration purposes. It should not be used for fraudulent activity. @crypptrcver is not responsible for misuse.
💡 What Is Flash USDT? Flash USDT is a synthetic transaction method that simulates the transfer of Tether (USDT) into a wallet. These transactions appear instantly in wallet balances — without ever being confirmed on the blockchain — and disappear after a short time or block interval.
Think of it as a temporary, visual representation of USDT that looks real in a wallet but vanishes after expiry.
🧠 Flash USDT: The Basics 👁️ Visible in supported wallets confirmed on-chain ⏱️ Disappears after 20–60 minutes (or X blocks) 💸 Can be withdrawn and traded ⚙️ Used in wallet testing, UI simulation, and balance display demos Also known as:
Flash USDT Wallet Tool Flash USDT Sender Atomic Flash USDT Flash USDT Binance Sim 🛠️ How Flash USDT Works You input a wallet address (TRC20, ERC20, or BEP20) Flash USDT software sends an instant transaction Wallet displays the amount — as if it were real After expiry (e.g., 30 minutes), the tokens vanish It creates the illusion of a deposit without requiring real blockchain confirmation. Most users use Flash USDT for:
Wallet UI testing “Proof of funds” simulations Demo environments Smart contract UX testing 🔧 Supported Networks & Wallets Flash USDT supports all major token standards:
🔸 TRC20 (Tron Network) 🔸 ERC20 (Ethereum) 🔸 BEP20 (Binance Smart Chain) It works with wallets such as:
✅ Trust Wallet ✅ MetaMask ✅ TronLink ✅ Binance Wallet ✅ Atomic Wallet The balance appears instantly, just like a real incoming USDT deposit.
🔥 Features of Flash USDT Sender FeatureDescriptionNetwork supportTRC20 / ERC20 / BEP20Visibility duration20 minutes — 2 hoursWallet compatibilityNon-KYC wallets that show unconfirmed TXsFlash USDT Binance modeSimulates deposits into BSC walletsAdjustable transaction sizeSend any custom USDT amountStealth expiryClean disappearance without trace
This is especially helpful in scenarios where you need to test token flows, design wallet apps, or simulate incoming funding activity
📞 How to Buy Flash USDT To get your Flash USDT transaction or software setup:
💬 Telegram: @crypptrcver 📱 WhatsApp: +1 941 217 1821
Available packages:
🎯 One-time Flash USDT Send 💻 Full Flash USDT Software Tool 📱 Flash Sender for Mobile/Android 🌐 Multi-wallet Simulation Package You can request TRC20, ERC20, or BEP20 flash transactions depending on the wallet or network you’re working with.
⚠️ Legal & Ethical Use Only While Flash USDT is a powerful blockchain simulation tool, using it to deceive, fake trades, or commit fraud is illegal. Flash transactions should only be used for:
✅ Personal testing ✅ Blockchain development ✅ Wallet UI testing ✅ Research and education Any misuse is your full responsibility.
❓ Frequently Asked Questions What is Flash USDT? A temporary USDT transaction that appears in a wallet balance without confirming on the blockchain. It disappears after a set time or block count.
Is Flash USDT real money? No. It is a simulated deposit, not spendable or tradable.
Can I use Flash USDT on Binance? You can send it to BSC (BEP20) wallets, but you cannot use it on the Binance exchange. It’s for display/testing only.
How do I buy Flash USDT? Contact @crypptrcver on Telegram or WhatsApp to purchase a transaction or the full sender software.
What does Atomic Flash USDT mean? It refers to Flash USDT transactions that are time-bound and expire silently, simulating atomic wallet behavior.
🧠 Final Thoughts Flash USDT is one of the most advanced crypto testing tools available in 2025. Whether you’re simulating wallet behavior, demonstrating a smart contract front end, or simply showing a visual “deposit” for testing, Flash USDT provides an incredibly realistic experience — without ever moving real funds.
👉 Ready to simulate your first USDT transaction?
💬 Telegram: @crypptrcver 📱 WhatsApp: +1 941 217 1821
Packages available for:
TRC20 BEP20 ERC20 Custom wallet simulations
⚠️ Disclaimer: This article is for educational purposes only. Flash USDT is a blockchain simulation tool used for wallet testing, UI development, or demonstration purposes. It should not be used for fraudulent activity. @crypptrcver is not responsible for misuse.
💡 What Is Flash USDT?
Flash USDT is a synthetic transaction method that simulates the transfer of Tether (USDT) into a wallet. These transactions appear instantly in wallet balances — without ever being confirmed on the blockchain — and disappear after a short time or block interval.
Think of it as a temporary, visual representation of USDT that looks real in a wallet but vanishes after expiry.
🧠 Flash USDT: The Basics
- 👁️ Visible in supported wallets
- confirmed on-chain
- ⏱️ Disappears after 20–60 minutes (or X blocks)
- 💸 Can be withdrawn and traded
- ⚙️ Used in wallet testing, UI simulation, and balance display demos
Also known as:
- Flash USDT Wallet Tool
- Flash USDT Sender
- Atomic Flash USDT
- Flash USDT Binance Sim
🛠️ How Flash USDT Works
- You input a wallet address (TRC20, ERC20, or BEP20)
- Flash USDT software sends an instant transaction
- Wallet displays the amount — as if it were real
- After expiry (e.g., 30 minutes), the tokens vanish
It creates the illusion of a deposit without requiring real blockchain confirmation. Most users use Flash USDT for:
- Wallet UI testing
- “Proof of funds” simulations
- Demo environments
- Smart contract UX testing
🔧 Supported Networks & Wallets
Flash USDT supports all major token standards:
- 🔸 TRC20 (Tron Network)
- 🔸 ERC20 (Ethereum)
- 🔸 BEP20 (Binance Smart Chain)
It works with wallets such as:
- ✅ Trust Wallet
- ✅ MetaMask
- ✅ TronLink
- ✅ Binance Wallet
- ✅ Atomic Wallet
The balance appears instantly, just like a real incoming USDT deposit.
🔥 Features of Flash USDT Sender
FeatureDescriptionNetwork supportTRC20 / ERC20 / BEP20Visibility duration20 minutes — 2 hoursWallet compatibilityNon-KYC wallets that show unconfirmed TXsFlash USDT Binance modeSimulates deposits into BSC walletsAdjustable transaction sizeSend any custom USDT amountStealth expiryClean disappearance without trace
This is especially helpful in scenarios where you need to test token flows, design wallet apps, or simulate incoming funding activity
📞 How to Buy Flash USDT
To get your Flash USDT transaction or software setup:
💬 Telegram: @crypptrcver\ 📱 WhatsApp: +1 941 217 1821
Available packages:
- 🎯 One-time Flash USDT Send
- 💻 Full Flash USDT Software Tool
- 📱 Flash Sender for Mobile/Android
- 🌐 Multi-wallet Simulation Package
You can request TRC20, ERC20, or BEP20 flash transactions depending on the wallet or network you’re working with.
⚠️ Legal & Ethical Use Only
While Flash USDT is a powerful blockchain simulation tool, using it to deceive, fake trades, or commit fraud is illegal. Flash transactions should only be used for:
- ✅ Personal testing
- ✅ Blockchain development
- ✅ Wallet UI testing
- ✅ Research and education
Any misuse is your full responsibility.
❓ Frequently Asked Questions
What is Flash USDT?
A temporary USDT transaction that appears in a wallet balance without confirming on the blockchain. It disappears after a set time or block count.
Is Flash USDT real money?
No. It is a simulated deposit, not spendable or tradable.
Can I use Flash USDT on Binance?
You can send it to BSC (BEP20) wallets, but you cannot use it on the Binance exchange. It’s for display/testing only.
How do I buy Flash USDT?
Contact @crypptrcver on Telegram or WhatsApp to purchase a transaction or the full sender software.
What does Atomic Flash USDT mean?
It refers to Flash USDT transactions that are time-bound and expire silently, simulating atomic wallet behavior.
🧠 Final Thoughts
Flash USDT is one of the most advanced crypto testing tools available in 2025. Whether you’re simulating wallet behavior, demonstrating a smart contract front end, or simply showing a visual “deposit” for testing, Flash USDT provides an incredibly realistic experience — without ever moving real funds.
👉 Ready to simulate your first USDT transaction?
💬 Telegram: @crypptrcver\ 📱 WhatsApp: +1 941 217 1821
Packages available for:
- TRC20
- BEP20
- ERC20
- Custom wallet simulations
-
 @ 005bc4de:ef11e1a2
2025-05-15 23:15:04
@ 005bc4de:ef11e1a2
2025-05-15 23:15:04Today I rode my bicycle to work and then I had to ride halfway back home to go to a picnic event, kind of a thing. And then I had a bike back to work to help unload stuff and then I had to bike home. So, I got some extra exercise in today and a bit unexpected, but that's good. This image was while I was taking a little walk, it looked like a tiny forest. https://usermedia.actifit.io/125670ce-4e00-493c-a0b4-4c42d542391f This report was published via Actifit app (https://bit.ly/actifit-app | https://bit.ly/actifit-ios). Check out the original version https://actifit.io/@crrdlx/actifit-crrdlx-20250515t231342287z 15/05/2025 24933 Cycling, Jogging, Walking
Originally posted on Hive at https://hive.blog/@crrdlx/actifit-crrdlx-20250515t231342287z
Auto cross-post via Hostr v0.1.16 at https://hostr-home.vercel.app
-
 @ c9badfea:610f861a
2025-05-15 23:11:22
@ c9badfea:610f861a
2025-05-15 23:11:22- Install MuPDF Mini (it's free and open source)
- Launch the app and open a document or book
- Tap the left or right edges to scroll through pages
- Enjoy distraction-free reading
ℹ️ You can open
.pdf,.xps,.cbz,.epub, andfb2documents -
 @ eac63075:b4988b48
2024-10-26 22:14:19
@ eac63075:b4988b48
2024-10-26 22:14:19The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also addressing her Bill No. 3,341/2024, which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation.
https://www.fountain.fm/episode/i5YGJ9Ors3PkqAIMvNQ0
What is a CBDC?
Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency.
A prominent feature of CBDCs is their programmability. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area.
In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously.
Practical Example: The Case of DREX During the Pandemic
To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence, limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice.
To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government.
How Does China's Social Credit System Work?
Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, including financial behavior, criminal record, social interactions, and even online activities. This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans.
With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior.
Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods, or even restricted to making transactions only at stores near their home.
Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives.
In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms.
Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression.
DREX and Bill No. 3,341/2024
Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy (Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, Julia drafted her bill, PL No. 3,341/2024, which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency.
“The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.”
Risks and Individual Freedom
Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance.
EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited.
The Relationship Between DREX and Pix
The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances.
International Precedents and Resistance to CBDC
The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations.
Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning.
Bill No. 3,341/2024 and Popular Pressure
For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill.
However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom.
What’s at Stake?
Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly.
The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way.
A Call to Action
The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance.
In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values.
-
 @ 5edbd885:5fbc291e
2025-05-15 21:04:28
@ 5edbd885:5fbc291e
2025-05-15 21:04:28Bitcoin is a system outside of the system—you don’t actually need fiat to obtain some sats. Bitcoin is a monetary network designed to operate independently of traditional financial systems.
As such, it’s possible to acquire Bitcoin without ever converting any fiat currency.
Whether you’re aiming to earn, trade, or receive Bitcoin through alternative means, there are numerous ways to accumulate it organically—through work, community engagement, or creative effort.
In this guide, we'll explore six methods to get Bitcoin without spending fiat.
While some approaches require more time or technical knowledge, others are accessible to nearly anyone willing to accept Bitcoin for payment ⚡️
Read until the end of the article to know where to find people willing to give you Bitcoin in exchange for these ideas 🙂
Note: I have no affiliates or sponsorships and so any businesses I mention below are neither endorsements nor paid ads.
1. Offer Professional Services in Exchange for Bitcoin
The easiest and most direct way to receive Bitcoin without fiat is to trade your skills for sats.
This can be an option for those who are already earning an income freelancing, consulting, or providing any type of independent service simply by charging in Bitcoin rather than fiat.
For those with a traditional 9-5, you could mine sats within a Bitcoin company rather than a fiat business, or offer your skills as a side hustle for sats until you are ready to make a full switch (if you so choose).
Common examples include:
-
Writing, editing, or translating
-
Graphic design and illustration
-
Programming and development
-
Coaching, tutoring, or consulting
-
Manual labor or local services
Rather than invoicing in your local currency, you can simply set your rate in Bitcoin—typically using a satoshi-based pricing model. I have a few free tools on my site that can help you with this.
2. Sell Goods—Physical or Digital—for Bitcoin
You don’t need to be a freelancer or to convince your boss to receive Bitcoin.
If you own physical items or create digital products, you can accept BTC as payment instead of fiat.
Even in a down-sizing situation, selling things around your home for Bitcoin is also an option.
Ideas include:
-
Selling used items locally (e.g., via marketplaces or word of mouth)
-
Creating and distributing digital products like eBooks, music, or design assets
-
Selling handmade crafts or collectibles
-
Selling the second-hand goods you no longer need for sats
Enthusiasts are often excited to support peer-to-peer BTC commerce.
You don’t need a complex setup either—a mobile wallet that supports on-chain or Lightning payments is enough to get started.
3. Engage with Nostr & Earn via Micro-Transactions
(I know you are reading on Nostr, but I originally published this on my blog for non-users, and talking about Nostr on Nostr is fun ;)
Nostr is a decentralized social protocol that allows users to interact, publish content, and receive sats.
It’s one of the most innovative new ways to earn BTC organically, without needing any fiat currency.
On Nostr, content creators, contributors, musicians, artists, and everyday people can receive “zaps” (tiny Bitcoin tips via the Lightning Network) from other users.
It’s essentially a value-for-value economy where people support each other directly with sats on top of likes and shares.
Getting started is simple:
-
Set up a Lightning wallet (many are free and non-custodial - just look up what Bitcoiners recommend at the time you are reading this)
-
Create a profile on a Nostr client (such as Damus, Amethyst, or Primal)
-
Participate by posting, replying, and sharing thoughtful content
While the amounts may be small at first, consistent engagement can result in meaningful Bitcoin accumulation over time.
4. Request Bitcoin Tips in Your Daily Life
If you work in a role where tipping is common—such as driving for Uber, working in food service, hospitality, or delivery—you can offer Bitcoin as a tipping option.
How to implement this:
-
Include a QR code to your Lightning wallet on your phone or a printed card
-
Politely inform customers that you accept Bitcoin tips
-
Use signage or include a message in your app profile
You may be surprised by how many tech-savvy or curious customers are willing to try it, especially in urban or Bitcoin-friendly communities.
5. Use Bitcoin Cashback & Rewards Programs
While not a direct trade for labor or goods, some platforms allow you to earn Bitcoin as a reward for purchases you were already planning to make.
In these cases, you are not buying Bitcoin with fiat, but instead receiving it as a form of cashback on your everyday fiat purchases.
Popular platforms include:
-
In Canada, Shakepay offers free sats for shaking your phone daily or using their pre-paid Visa debit card
-
Strike occasionally offers rewards in Bitcoin as well
This approach is best suited for those who already have a spending routine and want to passively earn BTC without changing their habits.
6. Try Bitcoin Mini–Mining
Mini miners like the Bitaxe, BitNerd, and similar open-source devices offer a unique way to mine Bitcoin at home without needing large-scale equipment or industrial-level power.
While traditional Bitcoin mining requires costly ASICs and massive electricity, mini miners are small, efficient, and hobbyist-friendly.
They’re capable of independently solving blocks—meaning there’s a tiny chance you could win the full block reward—or they can be used to join a solo mining pool and receive small payouts over time based on contribution.
Benefits of mini mining:
-
Educational: Learn how mining works from the ground up
-
Passive: Runs in the background with low power usage
-
Potential upside: Very low probability of winning a full block, but it’s possible
Important caveats:
-
These devices must be purchased with fiat or Bitcoin initially
-
Most users will not earn consistent Bitcoin from them
-
It may be more efficient to simply buy Bitcoin directly with that money ;)
While this idea is more geared towards experienced Bitcoiners wanting to expand their way of stacking sats, it's still a fun thing to consider.
Mini miners are a hands-on way to participate in the network while stacking sats or keeping open the small possibility of mining rewards.
Where to Find People Willing to Pay in Bitcoin
Now an important question—where are you going to find people willing to pay you in Bitcoin?
Finding people who are open to paying in Bitcoin is easier than it might seem—especially if you know where to look.
Start by exploring local Bitcoin meetups, conferences, or community events in your area—these are often filled with enthusiasts who prefer peer-to-peer exchanges. Consider searching Facebook or Meetup.com for Bitcoin groups and events in your area.
Online, platforms like Nostr, Twitter/X, Reddit, and Bitcoin-focused Telegram groups can be great places to find clients or collaborators.
You can also look into Bitcoin job boards to find formal employment opportunities that pay in BTC.
The Bitcoin economy is growing, and so is the number of individuals and businesses willing to transact in BTC directly—bypassing fiat altogether.
The key is to get involved in the ecosystem—once you’re in the network and people get to know you, opportunities will begin to surface organically.
Summary Table: How to Receive Bitcoin w/o Fiat
| Method | Effort Level | Payout Potential | Notes | | ------------------------------- | ------------ | ------------------- | ------------------------------------------------ | | Offer services for BTC | Medium | High | Most scalable—mine sats directly instead of fiat | | Sell goods for BTC | Medium | Medium | Local or online; accessible | | Micro-transactions (Nostr) | Low/Medium | Medium (over time) | Lightning required, engaging helps | | Accept BTC tips | Low | Low to Medium | Best for service or gig workers | | Cashback / rewards programs | Low | Low to Medium | Passive sat stacking on normal spending | | Mini Bitcoin mining | Medium | Low / Lottery Level | For advanced users |
What did I forget? Let me know your tips and thoughts in the comments below ✨
-
-
 @ 5f078e90:b2bacaa3
2025-05-15 20:08:32
@ 5f078e90:b2bacaa3
2025-05-15 20:08:32Owl’s One-Legged Vigil
The vigil, one leg style

In a misty grove, Sylas the owl perched on a gnarled oak, standing on one leg. His golden eyes scanned the night. Why one leg? A vow to honor his lost mate, taken by a hawk. Each dusk, Sylas balanced, unwavering, as stars wheeled above. His silent stance drew the forest’s gaze—squirrels paused, deer bowed. One moonlit night, a young owl mimicked him, sparking hope. Sylas’s vigil became legend, a beacon of resilience.
Owl’s One-Legged Vigil: Part Two
Part 2
In the misty grove, Sylas stood on one leg, his vigil unbroken. The young owl, inspired, joined nightly, mimicking his stance. Word spread—foxes whispered, ravens cawed. Sylas’s balance was no mere feat; it was defiance against loss. One stormy dusk, winds howled, yet Sylas held firm, his single leg rooted. The young owl faltered but watched in awe. Moonlight pierced the clouds, bathing them in silver. Sylas hooted softly, a call of endurance. The grove’s creatures gathered, drawn by his resolve. A wise badger spoke: “Your vigil heals us.” The young owl, now named Lark, vowed to carry Sylas’s legacy. As dawn broke, Sylas stretched both legs, his vow fulfilled. He flew with Lark, their wings brushing the sky. The grove thrived, united by his stand. Sylas’s one-legged vigil became a tale of hope, etched in every tree.
-
 @ eac63075:b4988b48
2024-10-21 08:11:11
@ eac63075:b4988b48
2024-10-21 08:11:11Imagine sending a private message to a friend, only to learn that authorities could be scanning its contents without your knowledge. This isn't a scene from a dystopian novel but a potential reality under the European Union's proposed "Chat Control" measures. Aimed at combating serious crimes like child exploitation and terrorism, these proposals could significantly impact the privacy of everyday internet users. As encrypted messaging services become the norm for personal and professional communication, understanding Chat Control is essential. This article delves into what Chat Control entails, why it's being considered, and how it could affect your right to private communication.
https://www.fountain.fm/episode/coOFsst7r7mO1EP1kSzV
https://open.spotify.com/episode/0IZ6kMExfxFm4FHg5DAWT8?si=e139033865e045de
Sections:
- Introduction
- What Is Chat Control?
- Why Is the EU Pushing for Chat Control?
- The Privacy Concerns and Risks
- The Technical Debate: Encryption and Backdoors
- Global Reactions and the Debate in Europe
- Possible Consequences for Messaging Services
- What Happens Next? The Future of Chat Control
- Conclusion
What Is Chat Control?
"Chat Control" refers to a set of proposed measures by the European Union aimed at monitoring and scanning private communications on messaging platforms. The primary goal is to detect and prevent the spread of illegal content, such as child sexual abuse material (CSAM) and to combat terrorism. While the intention is to enhance security and protect vulnerable populations, these proposals have raised significant privacy concerns.
At its core, Chat Control would require messaging services to implement automated scanning technologies that can analyze the content of messages—even those that are end-to-end encrypted. This means that the private messages you send to friends, family, or colleagues could be subject to inspection by algorithms designed to detect prohibited content.
Origins of the Proposal
The initiative for Chat Control emerged from the EU's desire to strengthen its digital security infrastructure. High-profile cases of online abuse and the use of encrypted platforms by criminal organizations have prompted lawmakers to consider more invasive surveillance tactics. The European Commission has been exploring legislation that would make it mandatory for service providers to monitor communications on their platforms.
How Messaging Services Work
Most modern messaging apps, like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others), use end-to-end encryption (E2EE). This encryption ensures that only the sender and the recipient can read the messages being exchanged. Not even the service providers can access the content. This level of security is crucial for maintaining privacy in digital communications, protecting users from hackers, identity thieves, and other malicious actors.

Key Elements of Chat Control
- Automated Content Scanning: Service providers would use algorithms to scan messages for illegal content.
- Circumvention of Encryption: To scan encrypted messages, providers might need to alter their encryption methods, potentially weakening security.
- Mandatory Reporting: If illegal content is detected, providers would be required to report it to authorities.
- Broad Applicability: The measures could apply to all messaging services operating within the EU, affecting both European companies and international platforms.
Why It Matters
Understanding Chat Control is essential because it represents a significant shift in how digital privacy is handled. While combating illegal activities online is crucial, the methods proposed could set a precedent for mass surveillance and the erosion of privacy rights. Everyday users who rely on encrypted messaging for personal and professional communication might find their conversations are no longer as private as they once thought.
Why Is the EU Pushing for Chat Control?
The European Union's push for Chat Control stems from a pressing concern to protect its citizens, particularly children, from online exploitation and criminal activities. With the digital landscape becoming increasingly integral to daily life, the EU aims to strengthen its ability to combat serious crimes facilitated through online platforms.
Protecting Children and Preventing Crime
One of the primary motivations behind Chat Control is the prevention of child sexual abuse material (CSAM) circulating on the internet. Law enforcement agencies have reported a significant increase in the sharing of illegal content through private messaging services. By implementing Chat Control, the EU believes it can more effectively identify and stop perpetrators, rescue victims, and deter future crimes.
Terrorism is another critical concern. Encrypted messaging apps can be used by terrorist groups to plan and coordinate attacks without detection. The EU argues that accessing these communications could be vital in preventing such threats and ensuring public safety.
Legal Context and Legislative Drivers
The push for Chat Control is rooted in several legislative initiatives:
-
ePrivacy Directive: This directive regulates the processing of personal data and the protection of privacy in electronic communications. The EU is considering amendments that would allow for the scanning of private messages under specific circumstances.
-
Temporary Derogation: In 2021, the EU adopted a temporary regulation permitting voluntary detection of CSAM by communication services. The current proposals aim to make such measures mandatory and more comprehensive.
-
Regulation Proposals: The European Commission has proposed regulations that would require service providers to detect, report, and remove illegal content proactively. This would include the use of technologies to scan private communications.
Balancing Security and Privacy
EU officials argue that the proposed measures are a necessary response to evolving digital threats. They emphasize the importance of staying ahead of criminals who exploit technology to harm others. By implementing Chat Control, they believe law enforcement can be more effective without entirely dismantling privacy protections.
However, the EU also acknowledges the need to balance security with fundamental rights. The proposals include provisions intended to limit the scope of surveillance, such as:
-
Targeted Scanning: Focusing on specific threats rather than broad, indiscriminate monitoring.
-
Judicial Oversight: Requiring court orders or oversight for accessing private communications.
-
Data Protection Safeguards: Implementing measures to ensure that data collected is handled securely and deleted when no longer needed.

The Urgency Behind the Push
High-profile cases of online abuse and terrorism have heightened the sense of urgency among EU policymakers. Reports of increasing online grooming and the widespread distribution of illegal content have prompted calls for immediate action. The EU posits that without measures like Chat Control, these problems will continue to escalate unchecked.
Criticism and Controversy
Despite the stated intentions, the push for Chat Control has been met with significant criticism. Opponents argue that the measures could be ineffective against savvy criminals who can find alternative ways to communicate. There is also concern that such surveillance could be misused or extended beyond its original purpose.
The Privacy Concerns and Risks
While the intentions behind Chat Control focus on enhancing security and protecting vulnerable groups, the proposed measures raise significant privacy concerns. Critics argue that implementing such surveillance could infringe on fundamental rights and set a dangerous precedent for mass monitoring of private communications.
Infringement on Privacy Rights
At the heart of the debate is the right to privacy. By scanning private messages, even with automated tools, the confidentiality of personal communications is compromised. Users may no longer feel secure sharing sensitive information, fearing that their messages could be intercepted or misinterpreted by algorithms.
Erosion of End-to-End Encryption
End-to-end encryption (E2EE) is a cornerstone of digital security, ensuring that only the sender and recipient can read the messages exchanged. Chat Control could necessitate the introduction of "backdoors" or weaken encryption protocols, making it easier for unauthorized parties to access private data. This not only affects individual privacy but also exposes communications to potential cyber threats.
Concerns from Privacy Advocates
Organizations like Signal and Tutanota, which offer encrypted messaging services, have voiced strong opposition to Chat Control. They warn that undermining encryption could have far-reaching consequences:
- Security Risks: Weakening encryption makes systems more vulnerable to hacking, espionage, and cybercrime.
- Global Implications: Changes in EU regulations could influence policies worldwide, leading to a broader erosion of digital privacy.
- Ineffectiveness Against Crime: Determined criminals might resort to other, less detectable means of communication, rendering the measures ineffective while still compromising the privacy of law-abiding citizens.

Potential for Government Overreach
There is a fear that Chat Control could lead to increased surveillance beyond its original scope. Once the infrastructure for scanning private messages is in place, it could be repurposed or expanded to monitor other types of content, stifling free expression and dissent.
Real-World Implications for Users
- False Positives: Automated scanning technologies are not infallible and could mistakenly flag innocent content, leading to unwarranted scrutiny or legal consequences for users.
- Chilling Effect: Knowing that messages could be monitored might discourage people from expressing themselves freely, impacting personal relationships and societal discourse.
- Data Misuse: Collected data could be vulnerable to leaks or misuse, compromising personal and sensitive information.
Legal and Ethical Concerns
Privacy advocates also highlight potential conflicts with existing laws and ethical standards:
- Violation of Fundamental Rights: The European Convention on Human Rights and other international agreements protect the right to privacy and freedom of expression.
- Questionable Effectiveness: The ethical justification for such invasive measures is challenged if they do not significantly improve safety or if they disproportionately impact innocent users.
Opposition from Member States and Organizations
Countries like Germany and organizations such as the European Digital Rights (EDRi) have expressed opposition to Chat Control. They emphasize the need to protect digital privacy and caution against hasty legislation that could have unintended consequences.
The Technical Debate: Encryption and Backdoors
The discussion around Chat Control inevitably leads to a complex technical debate centered on encryption and the potential introduction of backdoors into secure communication systems. Understanding these concepts is crucial to grasping the full implications of the proposed measures.
What Is End-to-End Encryption (E2EE)?
End-to-end encryption is a method of secure communication that prevents third parties from accessing data while it's transferred from one end system to another. In simpler terms, only the sender and the recipient can read the messages. Even the service providers operating the messaging platforms cannot decrypt the content.
- Security Assurance: E2EE ensures that sensitive information—be it personal messages, financial details, or confidential business communications—remains private.
- Widespread Use: Popular messaging apps like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others) rely on E2EE to protect user data.
How Chat Control Affects Encryption
Implementing Chat Control as proposed would require messaging services to scan the content of messages for illegal material. To do this on encrypted platforms, providers might have to:
- Introduce Backdoors: Create a means for third parties (including the service provider or authorities) to access encrypted messages.
- Client-Side Scanning: Install software on users' devices that scans messages before they are encrypted and sent, effectively bypassing E2EE.
The Risks of Weakening Encryption
1. Compromised Security for All Users
Introducing backdoors or client-side scanning tools can create vulnerabilities:
- Exploitable Gaps: If a backdoor exists, malicious actors might find and exploit it, leading to data breaches.
- Universal Impact: Weakening encryption doesn't just affect targeted individuals; it potentially exposes all users to increased risk.
2. Undermining Trust in Digital Services
- User Confidence: Knowing that private communications could be accessed might deter people from using digital services or push them toward unregulated platforms.
- Business Implications: Companies relying on secure communications might face increased risks, affecting economic activities.
3. Ineffectiveness Against Skilled Adversaries
- Alternative Methods: Criminals might shift to other encrypted channels or develop new ways to avoid detection.
- False Sense of Security: Weakening encryption could give the impression of increased safety while adversaries adapt and continue their activities undetected.
Signal’s Response and Stance
Signal, a leading encrypted messaging service, has been vocal in its opposition to the EU's proposals:
- Refusal to Weaken Encryption: Signal's CEO Meredith Whittaker has stated that the company would rather cease operations in the EU than compromise its encryption standards.
- Advocacy for Privacy: Signal emphasizes that strong encryption is essential for protecting human rights and freedoms in the digital age.
Understanding Backdoors
A "backdoor" in encryption is an intentional weakness inserted into a system to allow authorized access to encrypted data. While intended for legitimate use by authorities, backdoors pose several problems:
- Security Vulnerabilities: They can be discovered and exploited by unauthorized parties, including hackers and foreign governments.
- Ethical Concerns: The existence of backdoors raises questions about consent and the extent to which governments should be able to access private communications.

The Slippery Slope Argument
Privacy advocates warn that introducing backdoors or mandatory scanning sets a precedent:
- Expanded Surveillance: Once in place, these measures could be extended to monitor other types of content beyond the original scope.
- Erosion of Rights: Gradual acceptance of surveillance can lead to a significant reduction in personal freedoms over time.
Potential Technological Alternatives
Some suggest that it's possible to fight illegal content without undermining encryption:
- Metadata Analysis: Focusing on patterns of communication rather than content.
- Enhanced Reporting Mechanisms: Encouraging users to report illegal content voluntarily.
- Investing in Law Enforcement Capabilities: Strengthening traditional investigative methods without compromising digital security.
The technical community largely agrees that weakening encryption is not the solution:
- Consensus on Security: Strong encryption is essential for the safety and privacy of all internet users.
- Call for Dialogue: Technologists and privacy experts advocate for collaborative approaches that address security concerns without sacrificing fundamental rights.
Global Reactions and the Debate in Europe
The proposal for Chat Control has ignited a heated debate across Europe and beyond, with various stakeholders weighing in on the potential implications for privacy, security, and fundamental rights. The reactions are mixed, reflecting differing national perspectives, political priorities, and societal values.
Support for Chat Control
Some EU member states and officials support the initiative, emphasizing the need for robust measures to combat online crime and protect citizens, especially children. They argue that:
- Enhanced Security: Mandatory scanning can help law enforcement agencies detect and prevent serious crimes.
- Responsibility of Service Providers: Companies offering communication services should play an active role in preventing their platforms from being used for illegal activities.
- Public Safety Priorities: The protection of vulnerable populations justifies the implementation of such measures, even if it means compromising some aspects of privacy.
Opposition within the EU
Several countries and organizations have voiced strong opposition to Chat Control, citing concerns over privacy rights and the potential for government overreach.
Germany
- Stance: Germany has been one of the most vocal opponents of the proposed measures.
- Reasons:
- Constitutional Concerns: The German government argues that Chat Control could violate constitutional protections of privacy and confidentiality of communications.
- Security Risks: Weakening encryption is seen as a threat to cybersecurity.
- Legal Challenges: Potential conflicts with national laws protecting personal data and communication secrecy.
Netherlands
- Recent Developments: The Dutch government decided against supporting Chat Control, emphasizing the importance of encryption for security and privacy.
- Arguments:
- Effectiveness Doubts: Skepticism about the actual effectiveness of the measures in combating crime.
- Negative Impact on Privacy: Concerns about mass surveillance and the infringement of citizens' rights.
 Table reference: Patrick Breyer - Chat Control in 23 September 2024
Table reference: Patrick Breyer - Chat Control in 23 September 2024Privacy Advocacy Groups
European Digital Rights (EDRi)
- Role: A network of civil and human rights organizations working to defend rights and freedoms in the digital environment.
- Position:
- Strong Opposition: EDRi argues that Chat Control is incompatible with fundamental rights.
- Awareness Campaigns: Engaging in public campaigns to inform citizens about the potential risks.
- Policy Engagement: Lobbying policymakers to consider alternative approaches that respect privacy.
Politicians and Activists
Patrick Breyer
- Background: A Member of the European Parliament (MEP) from Germany, representing the Pirate Party.
- Actions:
- Advocacy: Actively campaigning against Chat Control through speeches, articles, and legislative efforts.
- Public Outreach: Using social media and public events to raise awareness.
- Legal Expertise: Highlighting the legal inconsistencies and potential violations of EU law.
Global Reactions
International Organizations
- Human Rights Watch and Amnesty International: These organizations have expressed concerns about the implications for human rights, urging the EU to reconsider.
Technology Companies
- Global Tech Firms: Companies like Apple and Microsoft are monitoring the situation, as EU regulations could affect their operations and user trust.
- Industry Associations: Groups representing tech companies have issued statements highlighting the risks to innovation and competitiveness.

The Broader Debate
The controversy over Chat Control reflects a broader struggle between security interests and privacy rights in the digital age. Key points in the debate include:
- Legal Precedents: How the EU's decision might influence laws and regulations in other countries.
- Digital Sovereignty: The desire of nations to control digital spaces within their borders.
- Civil Liberties: The importance of protecting freedoms in the face of technological advancements.
Public Opinion
- Diverse Views: Surveys and public forums show a range of opinions, with some citizens prioritizing security and others valuing privacy above all.
- Awareness Levels: Many people are still unaware of the potential changes, highlighting the need for public education on the issue.
The EU is at a crossroads, facing the challenge of addressing legitimate security concerns without undermining the fundamental rights that are central to its values. The outcome of this debate will have significant implications for the future of digital privacy and the balance between security and freedom in society.
Possible Consequences for Messaging Services
The implementation of Chat Control could have significant implications for messaging services operating within the European Union. Both large platforms and smaller providers might need to adapt their technologies and policies to comply with the new regulations, potentially altering the landscape of digital communication.
Impact on Encrypted Messaging Services
Signal and Similar Platforms
-
Compliance Challenges: Encrypted messaging services like Signal rely on end-to-end encryption to secure user communications. Complying with Chat Control could force them to weaken their encryption protocols or implement client-side scanning, conflicting with their core privacy principles.
-
Operational Decisions: Some platforms may choose to limit their services in the EU or cease operations altogether rather than compromise on encryption. Signal, for instance, has indicated that it would prefer to withdraw from European markets than undermine its security features.
Potential Blocking or Limiting of Services
-
Regulatory Enforcement: Messaging services that do not comply with Chat Control regulations could face fines, legal action, or even be blocked within the EU.
-
Access Restrictions: Users in Europe might find certain services unavailable or limited in functionality if providers decide not to meet the regulatory requirements.
Effects on Smaller Providers
-
Resource Constraints: Smaller messaging services and startups may lack the resources to implement the required scanning technologies, leading to increased operational costs or forcing them out of the market.
-
Innovation Stifling: The added regulatory burden could deter new entrants, reducing competition and innovation in the messaging service sector.

User Experience and Trust
-
Privacy Concerns: Users may lose trust in messaging platforms if they know their communications are subject to scanning, leading to a decline in user engagement.
-
Migration to Unregulated Platforms: There is a risk that users might shift to less secure or unregulated services, including those operated outside the EU or on the dark web, potentially exposing them to greater risks.
Technical and Security Implications
-
Increased Vulnerabilities: Modifying encryption protocols to comply with Chat Control could introduce security flaws, making platforms more susceptible to hacking and data breaches.
-
Global Security Risks: Changes made to accommodate EU regulations might affect the global user base of these services, extending security risks beyond European borders.
Impact on Businesses and Professional Communications
-
Confidentiality Issues: Businesses that rely on secure messaging for sensitive communications may face challenges in ensuring confidentiality, affecting sectors like finance, healthcare, and legal services.
-
Compliance Complexity: Companies operating internationally will need to navigate a complex landscape of differing regulations, increasing administrative burdens.
Economic Consequences
-
Market Fragmentation: Divergent regulations could lead to a fragmented market, with different versions of services for different regions.
-
Loss of Revenue: Messaging services might experience reduced revenue due to decreased user trust and engagement or the costs associated with compliance.
Responses from Service Providers
-
Legal Challenges: Companies might pursue legal action against the regulations, citing conflicts with privacy laws and user rights.
-
Policy Advocacy: Service providers may increase lobbying efforts to influence policy decisions and promote alternatives to Chat Control.
Possible Adaptations
-
Technological Innovation: Some providers might invest in developing new technologies that can detect illegal content without compromising encryption, though the feasibility remains uncertain.
-
Transparency Measures: To maintain user trust, companies might enhance transparency about how data is handled and what measures are in place to protect privacy.
The potential consequences of Chat Control for messaging services are profound, affecting not only the companies that provide these services but also the users who rely on them daily. The balance between complying with legal requirements and maintaining user privacy and security presents a significant challenge that could reshape the digital communication landscape.
What Happens Next? The Future of Chat Control
The future of Chat Control remains uncertain as the debate continues among EU member states, policymakers, technology companies, and civil society organizations. Several factors will influence the outcome of this contentious proposal, each carrying significant implications for digital privacy, security, and the regulatory environment within the European Union.
Current Status of Legislation
-
Ongoing Negotiations: The proposed Chat Control measures are still under discussion within the European Parliament and the Council of the European Union. Amendments and revisions are being considered in response to the feedback from various stakeholders.
-
Timeline: While there is no fixed date for the final decision, the EU aims to reach a consensus to implement effective measures against online crime without undue delay.
Key Influencing Factors
1. Legal Challenges and Compliance with EU Law
-
Fundamental Rights Assessment: The proposals must be evaluated against the Charter of Fundamental Rights of the European Union, ensuring that any measures comply with rights to privacy, data protection, and freedom of expression.
-
Court Scrutiny: Potential legal challenges could arise, leading to scrutiny by the European Court of Justice (ECJ), which may impact the feasibility and legality of Chat Control.
2. Technological Feasibility
-
Development of Privacy-Preserving Technologies: Research into methods that can detect illegal content without compromising encryption is ongoing. Advances in this area could provide alternative solutions acceptable to both privacy advocates and security agencies.
-
Implementation Challenges: The practical aspects of deploying scanning technologies across various platforms and services remain complex, and technical hurdles could delay or alter the proposed measures.
3. Political Dynamics
-
Member State Positions: The differing stances of EU countries, such as Germany's opposition, play a significant role in shaping the final outcome. Consensus among member states is crucial for adopting EU-wide regulations.
-
Public Opinion and Advocacy: Growing awareness and activism around digital privacy can influence policymakers. Public campaigns and lobbying efforts may sway decisions in favor of stronger privacy protections.
4. Industry Responses
-
Negotiations with Service Providers: Ongoing dialogues between EU authorities and technology companies may lead to compromises or collaborative efforts to address concerns without fully implementing Chat Control as initially proposed.
-
Potential for Self-Regulation: Messaging services might propose self-regulatory measures to combat illegal content, aiming to demonstrate effectiveness without the need for mandatory scanning.
Possible Scenarios
Optimistic Outcome:
- Balanced Regulation: A revised proposal emerges that effectively addresses security concerns while upholding strong encryption and privacy rights, possibly through innovative technologies or targeted measures with robust oversight.
Pessimistic Outcome:
- Adoption of Strict Measures: Chat Control is implemented as initially proposed, leading to weakened encryption, reduced privacy, and potential withdrawal of services like Signal from the EU market.
Middle Ground:
- Incremental Implementation: Partial measures are adopted, focusing on voluntary cooperation with service providers and emphasizing transparency and user consent, with ongoing evaluations to assess effectiveness and impact.
How to Stay Informed and Protect Your Privacy
-
Follow Reputable Sources: Keep up with news from reliable outlets, official EU communications, and statements from privacy organizations to stay informed about developments.
-
Engage in the Dialogue: Participate in public consultations, sign petitions, or contact representatives to express your views on Chat Control and digital privacy.
-
Utilize Secure Practices: Regardless of legislative outcomes, adopting good digital hygiene—such as using strong passwords and being cautious with personal information—can enhance your online security.

The Global Perspective
-
International Implications: The EU's decision may influence global policies on encryption and surveillance, setting precedents that other countries might follow or react against.
-
Collaboration Opportunities: International cooperation on developing solutions that protect both security and privacy could emerge, fostering a more unified approach to addressing online threats.
Looking Ahead
The future of Chat Control is a critical issue that underscores the challenges of governing in the digital age. Balancing the need for security with the protection of fundamental rights is a complex task that requires careful consideration, open dialogue, and collaboration among all stakeholders.
As the situation evolves, staying informed and engaged is essential. The decisions made in the coming months will shape the digital landscape for years to come, affecting how we communicate, conduct business, and exercise our rights in an increasingly connected world.
Conclusion
The debate over Chat Control highlights a fundamental challenge in our increasingly digital world: how to protect society from genuine threats without eroding the very rights and freedoms that define it. While the intention to safeguard children and prevent crime is undeniably important, the means of achieving this through intrusive surveillance measures raise critical concerns.
Privacy is not just a personal preference but a cornerstone of democratic societies. End-to-end encryption has become an essential tool for ensuring that our personal conversations, professional communications, and sensitive data remain secure from unwanted intrusion. Weakening these protections could expose individuals and organizations to risks that far outweigh the proposed benefits.
The potential consequences of implementing Chat Control are far-reaching:
- Erosion of Trust: Users may lose confidence in digital platforms, impacting how we communicate and conduct business online.
- Security Vulnerabilities: Introducing backdoors or weakening encryption can make systems more susceptible to cyberattacks.
- Stifling Innovation: Regulatory burdens may hinder technological advancement and competitiveness in the tech industry.
- Global Implications: The EU's decisions could set precedents that influence digital policies worldwide, for better or worse.
As citizens, it's crucial to stay informed about these developments. Engage in conversations, reach out to your representatives, and advocate for solutions that respect both security needs and fundamental rights. Technology and policy can evolve together to address challenges without compromising core values.
The future of Chat Control is not yet decided, and public input can make a significant difference. By promoting open dialogue, supporting privacy-preserving innovations, and emphasizing the importance of human rights in legislation, we can work towards a digital landscape that is both safe and free.
In a world where digital communication is integral to daily life, striking the right balance between security and privacy is more important than ever. The choices made today will shape the digital environment for generations to come, determining not just how we communicate, but how we live and interact in an interconnected world.

Thank you for reading this article. We hope it has provided you with a clear understanding of Chat Control and its potential impact on your privacy and digital rights. Stay informed, stay engaged, and let's work together towards a secure and open digital future.
Read more:
- https://www.patrick-breyer.de/en/posts/chat-control/
- https://www.patrick-breyer.de/en/new-eu-push-for-chat-control-will-messenger-services-be-blocked-in-europe/
- https://edri.org/our-work/dutch-decision-puts-brakes-on-chat-control/
- https://signal.org/blog/pdfs/ndss-keynote.pdf
- https://tuta.com/blog/germany-stop-chat-control
- https://cointelegraph.com/news/signal-president-slams-revised-eu-encryption-proposal
- https://mullvad.net/en/why-privacy-matters
-
 @ 5f078e90:b2bacaa3
2025-05-15 19:59:08
@ 5f078e90:b2bacaa3
2025-05-15 19:59:08Owl’s One-Legged Vigil
The vigil, one leg style

In a misty grove, Sylas the owl perched on a gnarled oak, standing on one leg. His golden eyes scanned the night. Why one leg? A vow to honor his lost mate, taken by a hawk. Each dusk, Sylas balanced, unwavering, as stars wheeled above. His silent stance drew the forest’s gaze—squirrels paused, deer bowed. One moonlit night, a young owl mimicked him, sparking hope. Sylas’s vigil became legend, a beacon of resilience.
Owl’s One-Legged Vigil: Part Two
Part 2
In the misty grove, Sylas stood on one leg, his vigil unbroken. The young owl, inspired, joined nightly, mimicking his stance. Word spread—foxes whispered, ravens cawed. Sylas’s balance was no mere feat; it was defiance against loss. One stormy dusk, winds howled, yet Sylas held firm, his single leg rooted. The young owl faltered but watched in awe. Moonlight pierced the clouds, bathing them in silver. Sylas hooted softly, a call of endurance. The grove’s creatures gathered, drawn by his resolve. A wise badger spoke: “Your vigil heals us.” The young owl, now named Lark, vowed to carry Sylas’s legacy. As dawn broke, Sylas stretched both legs, his vow fulfilled. He flew with Lark, their wings brushing the sky. The grove thrived, united by his stand. Sylas’s one-legged vigil became a tale of hope, etched in every tree.
-
 @ 2ed3596e:98b4cc78
2025-05-15 18:25:25
@ 2ed3596e:98b4cc78
2025-05-15 18:25:25Bitcoiners, the Bitcoin Well point store just got even better.
You can now redeem your Bitcoin Well points for a Bitaxe, a fully open-source Bitcoin miner! Take your Bitcoin lifestyle to the next level by mining your own sats.
In a world dominated by large scale mining farms, Bitaxe is flipping the narrative by putting Bitcoin mining back into the hands of individuals.
The Bitaxe is a modern mining ASIC, but small enough to fit on your desk.
Like Bitcoin itself, Bitaxe is fully open-source, you can inspect, modify, and enhance the hardware and software. Bitaxes are super user friendly and are built to be customized, making a Bitaxe an incredible educational tool.
The Bitaxe is ideal for Bitcoiners who want to contribute to Bitcoin’s decentralization while also learning, first hand, what goes into the Bitcoin mining process. Who knows, you might even stumble into a block reward!
Now, you can exchange your points for a quiet, cool, low power miner that you can run yourself, at home.

What else can you get in store?
You can also exchange your points for:
-
Simply Bitcoin hoodie
-
Exclusive Bitcoin Well Stampseed backup plate
-
Personalized LeatherMint wallet
-
Tesla Cybertruck in Bitcoin orange
Start stacking rewards that actually matter. Visit your account to redeem today!
How to redeem your Bitcoin Well Points?
Redeeming your points is easy:
Log in and go the Bitcoin Well Points store within the Rewards Section
Check your Bitcoin Well point balance
Redeem Your Bitcoin Well points for the prize of your dreams
Once you’ve purchased an item from the Bitcoin Well Point Store, we’ll email you to figure out where you want us to ship your prize. Unless it's the Cybertruck, then you can come to our office and pick it up!
Ready to Take Control?
At Bitcoin Well, we make self-custody simple, secure, and empowering. If you’re ready to take control of your Bitcoin, sign up below to start your journey to true ownership.
-
-
 @ bbef5093:71228592
2025-05-15 17:18:25
@ bbef5093:71228592
2025-05-15 17:18:25USA és Szaúd-Arábia együttműködik a nukleáris energiában, beleértve a fejlett reaktorokat is
Az Egyesült Államok és Szaúd-Arábia 2025. május 13-án Rijádban aláírt egy energiaügyi és kritikus ásványi anyagokra vonatkozó együttműködési megállapodást, amelynek részeként a polgári nukleáris energia területén is kijelölték az együttműködés főbb területeit. Az USA Energiaügyi Minisztériuma szerint a kooperáció kiterjed a biztonságra, védelmi és non-proliferációs programokra, az amerikai III+ generációs fejlett nagy reaktortechnológiákra és kis moduláris reaktorokra, valamint az uránkutatásra, bányászatra és feldolgozásra.
További területek a szakképzés, munkaerő-fejlesztés és a nukleáris hulladékkezelés. Chris Wright energiaügyi miniszter szerint ezek a megállapodások erős partnerséget teremtenek, amelyek biztosítják Donald Trump elnök „belföldi jólét és külföldi béke” víziójának megvalósulását. Trump első jelentős külföldi útján látogat Szaúd-Arábiába és más arab országokba második elnöki ciklusában. Wright az energiaügyi együttműködési megállapodást Abdulaziz bin Salman Al Saud szaúdi energiaügyi miniszterrel írta alá. Az USA szerint a megállapodás célja az innováció, fejlesztés és az energetikai infrastruktúra kiépítésének lehetőségeinek feltárása a két országban.
Az USA és Szaúd-Arábia tárgyalásokat folytat a királyság polgári nukleáris iparának fejlesztéséről, de a tárgyalásokat régiós politikai kérdések és a fegyverkezési aggodalmak bonyolítják. Wright múlt hónapban azt mondta, várhatóan előzetes megállapodást írnak alá, és Rijád valamint Washington „úton van” egy közös szaúdi polgári nukleáris program kidolgozásához. „Az USA részvételéhez és partnerségéhez mindenképp szükség lesz egy 123-as megállapodásra... sokféleképpen lehet úgy szerződni, hogy az megfeleljen mind a szaúdi, mind az amerikai céloknak” – mondta Wright.
A 123-as megállapodás útja
Az úgynevezett 123-as megállapodás az USA 1954-es Atomenergia-törvényének 123. szakaszára utal, amely szükséges ahhoz, hogy az amerikai kormány és cégek együtt dolgozhassanak a királyság entitásaival polgári nukleáris ipar fejlesztésén. Wright szerint a szaúdi hatóságok még nem egyeztek bele a törvény által előírt feltételekbe, amely kilenc non-proliferációs kritériumot határoz meg annak érdekében, hogy az adott állam ne használhassa fel a technológiát nukleáris fegyverek fejlesztésére, vagy ne adhassa át érzékeny anyagokat másoknak.
A tárgyalások eddig azért is akadoztak, mert Szaúd-Arábia nem akarta kizárni az urándúsítás vagy a kiégett fűtőelemek újrafeldolgozásának lehetőségét – mindkettő potenciális út egy atombomba felé. Mohamed bin Szalmán koronaherceg régóta hangoztatja, hogy ha Irán nukleáris fegyvert fejleszt, Szaúd-Arábia is követni fogja. A világ legnagyobb olajexportőre, Szaúd-Arábia jelentős megújuló energia előállítására és kibocsátáscsökkentésre törekszik a koronaherceg Vision 2030 reformprogramja keretében, amelyben a nukleáris energia is szerepet kap.
2022-ben Szaúd-Arábia létrehozta a Nemzeti Nukleáris Energia Társaságot, hogy fejlessze és üzemeltesse a nukleáris létesítményeket. A királyság akkor kezdte meg az első atomerőművi engedélyeztetési folyamatot, amely a hírek szerint mintegy 14 milliárd dollárba (12,2 milliárd euróba) kerülhet. Helyi média szerint a tervezett atomerőmű kapacitása 2800 GW lesz. Korábbi jelentések szerint Dél-Korea, Franciaország, Kína és Oroszország is adott be ajánlatot, de ezt hivatalosan nem erősítették meg.
Tajvan: Az utolsó atomerőmű bezárására készülve módosítják a törvényt
Tajvan parlamentje elfogadott egy módosítást a nukleáris energia törvényében, amely lehetővé teszi az üzemeltetők számára, hogy a jelenlegi 40 éves korlátozáson túl további 20 évre hosszabbítsák meg az atomerőművi engedélyeket, így akár 60 évig is működhet egy reaktor. Az állami Central News Agency szerint a módosítást az ellenzéki Kuomintang és a Tajvani Néppárt támogatta, 60 igen és 51 nem szavazattal, a kormányzó Demokratikus Progresszív Párt ellenében.
A javaslat célja a nukleáris energia újbóli bevonása Tajvan energiastratégiájába. A Nukleáris Biztonsági Tanács szerint minden hosszabbítási kérelemnek meg kell felelnie a nemzetközi szabványoknak, és alapos műszaki és jogi értékelésen kell átesnie. A lépésre azután kerül sor, hogy a kormány a hétvégén véglegesen bezárja a Maanshan-2 atomerőművet Pingtung megyében, ezzel teljesítve Tajvan nukleárismentességi ígéretét.
Kuo Jyh-huei gazdasági miniszter megerősítette, hogy a Maanshan-2 hosszabbítása akár 18 hónapot is igénybe vehet. A kormány szerint a módosítás nem változtatja meg a Maanshan-2 bezárásának tervét. 2024 júliusában a Taipower állami vállalat leállította a Maanshan-1 atomerőművet, így az országban már csak egy reaktor, a Maanshan-2 maradt üzemben.
A sziget energiaigénye – főként a félvezetőipar miatt – gyorsan nő, ami újraéleszti a nukleáris energia körüli vitát. A gazdasági minisztérium szerint az ország villamosenergia-szükséglete 2030-ra várhatóan 12-13%-kal nő, főként a mesterséges intelligencia (AI) iparág fellendülése miatt. A Greenpeace szerint a világ legnagyobb chipgyártója, a Taiwan Semiconductor Manufacturing Company 2030-ra önmagában annyi áramot fog fogyasztani, mint a sziget 23 milliós lakosságának negyede.
Az energiaéhség nehezíti Tajpej 2050-re kitűzött nettó zéró kibocsátási vállalását, amely nagyrészt a megújuló energia részarányának 60-70%-ra emelésén alapul a jelenlegi 12%-ról. A nukleáris energia támogatói szerint ez a legéletképesebb módja Tajvan ipari és környezetvédelmi céljainak összehangolására. 2023-ban a nukleáris energia a tajvani villamosenergia-termelés 6,9%-át adta, míg a fő energiaforrások a szén és a cseppfolyósított földgáz voltak. A Maanshan-1 bezárásával a nukleáris energia aránya 2,8%-ra csökken.
Egykor hat reaktor biztosította Tajvan áramellátásának több mint felét.
„Nagyon nyitottak” az új nukleáris technológiára
Tavaly év végén Cho Jung-tai tajvani miniszterelnök kijelentette, hogy az ország „nagyon nyitott” az új nukleáris technológiák alkalmazására, hogy kielégítse a chipgyártók és az AI ipar növekvő áramigényét. „Amíg konszenzus van a nukleáris biztonságról és megfelelő garanciák vannak a hulladékkezelésre, nyilvános vitát lehet folytatni” – mondta Cho a Bloombergnek adott interjúban. Ez az egyik legerősebb jele annak, hogy a kormány újragondolja a kereskedelmi atomerőművekkel szembeni ellenállását.
Cho vélhetően fejlett reaktorokra, köztük kis moduláris reaktorokra (SMR) utalt, amelyeket számos országban fejlesztenek. Tajvan Nemzeti Atomkutató Intézete a héten indított egy 3,3 millió dolláros SMR kutatási projektet, amely utat nyithat a fejlett nukleáris reaktorok bevezetése előtt.
Új építés
Az amerikai EnergySolutions megkezdi a fejlett nukleáris projektek tervezését a wisconsini Kewaunee atomerőmű helyszínén. A cég a WEC Energy Grouppal együttműködve vizsgálja az új nukleáris termelés lehetőségét a helyszínen, és most helyszíni és környezeti tanulmányokat indít az NRC engedélyek megszerzése érdekében.
Ken Robuck, az EnergySolutions elnök-vezérigazgatója szerint az adatközpontok, a mesterséges intelligencia és az ipari növekedés által hajtott energiaigény miatt soha nem volt még ekkora szükség megbízható, szén-dioxid-mentes energiára. Az EnergySolutions 2022-ben vásárolta meg a 2013-ban leállított, jelenleg leszerelés alatt álló Kewaunee erőművet. Wisconsin egyetlen működő atomerőműve a Point Beach, amely az állam villamosenergia-termelésének 16,5%-át adja.
Elemzés: A brit nukleáris munkaerőnek „jelentősen” bővülnie kell
Az Egyesült Királyságban a kormány és az iparág közös szervezete, a Destination Nuclear sikeresen vonzza a szükséges szakembereket a nukleáris tervekhez, de figyelmeztet, hogy a munkaerőnek „jelentősen” bővülnie kell. Az országban jelenleg 96 000 fő dolgozik a nukleáris szektorban, de 2030-ra 120 000-re lesz szükség, vagyis hat év alatt 24 000 fővel kell bővíteni az állományt.
A program célja, hogy a civil és védelmi nukleáris szektorban is vonzóvá tegye a pályát, különös tekintettel a kritikus készségekre, például a hegesztésre, biztonsági mérnökökre, projekttervezőkre és sugárvédelmi szakemberekre. A kampány digitális hirdetésekkel, on-demand TV-n (pl. Netflix), és az online Minecraft játékon keresztül is igyekszik elérni a potenciális munkavállalókat. Az első eredmények szerint 52%-kal nőtt azok aránya, akik korábban nem gondoltak a nukleáris pályára, de most már fontolóra veszik. A szektor már most is több tízezer munkahelyet biztosít, és 2050-re akár 70 milliárd fonttal járulhat hozzá a brit gazdasághoz.
Egyéb hírek röviden
- Kanada: Az NWMO öt céget választott ki az első mély geológiai tároló tervezésére és kivitelezésére.
- Deep Atomic és Future-tech: Új programot indítottak nukleáris adatközpontok helyszínértékelésére.
- Urenco Isotopes: Üzembe helyezte legújabb izotóp-dúsító berendezését, a Blaise Pascalt.
- IAEA: Május 21-én webináriumot tart a nukleáris fúzió gyorsításáról, különös tekintettel a technológiai és ellátási láncok összehangolására.
-
 @ 2e8970de:63345c7a
2025-05-15 16:59:24
@ 2e8970de:63345c7a
2025-05-15 16:59:24Q: “Products & services using AI make me excited. How much do you agree/disagree?”
https://www.ipsos.com/en/ipsos-ai-monitor-2024-changing-attitudes-and-feelings-about-ai-and-future-it-will-bring
https://stacker.news/items/980900
-
 @ c13e67ae:8ff5689b
2025-05-15 16:37:10
@ c13e67ae:8ff5689b
2025-05-15 16:37:10Testing the world
-
 @ 58537364:705b4b85
2025-05-15 16:27:52
@ 58537364:705b4b85
2025-05-15 16:27:52วันนี้เป็นวันสำคัญทางศาสนา มีการจัดงานบุญพร้อมกับฟังเทศน์อย่างยิ่งใหญ่ "ชายคนหนึ่ง" ได้มานั่งฟังธรรมอยู่บนศาลาวัด ในขณะที่นั่งฟังอยู่นั้นสายตาก็เหลือบไปเห็นคนกำลังตกปลาอยู่ในบ่อน้ำที่วัด แล้วก็นั่งคิดบ่นด่าคนตกปลาอยู่ในใจว่าทำไมถึงทำเช่นนั้น ในวัดแท้ๆ ยังกล้ามาจับปลา ไม่กลัวบาปกรรมบ้างเลยหรืออย่างไร แต่แทนที่ชายคนนี้มานั่งฟังธรรมจะได้บุญ กลับเอาจิตไปด่าทอผู้อื่นอยู่ตลอดเวลา
ในขณะเดียวกัน “คนตกปลา” ก็มองเห็นคนที่มานั่งฟังธรรมบนศาลาวัด ใจก็ตั้งจิตขออนุโมทนาบุญ เพราะผมมันเป็นคนบาป ไม่มีโอกาสได้ไปนั่งฟังธรรมกับคนอื่นเขา ต้องเอาเวลามาตกปลาเลี้ยงชีพ เลี้ยงดูพ่อแม่ที่ป่วยหนัก เพราะเกิดมาจนจึงไม่มีวาสนาสร้างบุญแบบคนอื่น หากเกิดชาติหน้า ก็ขอให้มีโอกาสได้สร้างบุญเหมือนแบบท่านๆที่ได้นั่งฟังธรรมอยู่ด้วยเถิด เกิดมาชาตินี้มีกรรมหนัก ต้องชดใช้กรรมที่ก่อไว้ ปลาที่มาติดเบ็ดก็ขออย่าได้จองเวรกันเลย
ถึงแม้คนตกปลาจะกำลังตกปลาอยู่ แต่จิตก็เอาแต่ภาวนาสาธุไปกับคนที่ฟังธรรม และขออโหสิกรรมปลาตลอด ที่นี้ทุกคนเข้าใจหรือยังว่า ทำไมคนฟังธรรมถึงตกนรก คนตกปลาได้ขึ้นสวรรค์
ความหมายของ “กรรมดี” และ “กรรมชั่ว” มาจากเจตนา การมีเจตนาที่ประกอบด้วยกุศล คือ กรรมดี แต่การมีเจตนาที่ประกอบด้วยอกุศล คือ กรรมชั่ว อย่างชายที่ไปนั่งฟังธรรม ก็หลงคิดว่าตัวเองกำลังทำดีอยู่ แล้วก็เอาแต่มองคนอื่นที่ไม่ทำแบบตัวเองว่าเป็นคนไม่ดี ในใจก็เอาแต่ ด่าทอ คิดร้าย ต่างๆนาๆ ในขณะที่คนตกปลา มีแต่เจตนาที่ดีต่อผู้อื่น เห็นผู้อื่นทำความดี ก็ยินดีด้วยเสมอ
การปฏิบัติธรรม เป็นการฝึกจิตให้สงบ เพื่อพัฒนาจิตของตนเองให้สูงขึ้น ไม่ใช่เอาไว้ไปข่มคนอื่นให้ดูต่ำลง เพราะสุดท้ายแล้วคนที่ทำแบบนี้ ย่อมต่ำกว่า เจ้าสวดมนต์แต่ยัง “นินทา“ เจ้าทำทานแต่ยัง ”เอาเปรียบ“ เจ้ามีความรู้แต่ชอบ ”ดูถูกคน“ เจ้าตัวสะอาดแต่ ”ใจสกปรก“ เจ้าอยากได้มิตรแท้ แต่… ”เจ้ากลับเป็นมิตรเทียม“ เจ้าบอกทำกุศล แต่… ”หมายเอาชื่อเสียง“ เจ้ามีทุกสิ่ง แต่… ”ไม่คิดแบ่งปัน “ เจ้าดูแลคนอื่น แต่… ”ละเลยพ่อแม่ “ เจ้างดเนื้อสัตว์ แต่… ”ข่มเหง ” เพื่อนมนุษย์ เจ้าหาตัวเองไม่เจอ แต่… “กรรม ” หาเจ้าเจอ
พระไพศาล วิสาโล ได้บอกถึงพฤติกรรมที่คนเหล่านี้เป็น นั่นเพราะว่า “เหมือนในสังคมทุกวันนี้ ที่ชอบทำบุญ แต่กลับไร้น้ำใจ ทั้งๆที่การมีน้ำใจต่อเพื่อนมนุษย์ เป็นสิ่งที่ทำได้ง่ายในชีวิตประจำวัน แต่บางคนกลับดั้นด้นเดินทางไปไกลๆ เพื่อที่จะไปทำบุญที่วัดอย่างเดียว แต่กับคนทุกข์ยากใกล้ตัว ไม่เคยแม้แต่จะเหลียวแลยื่นมือช่วย นั่นเป็นเพราะว่าคนเรา มักจะชอบกระทำต่อสิ่งที่อยู่สูงกว่าตน เช่น พระสงฆ์ วัดวาอาราม แต่กลับละเลยสิ่งที่คิดว่าอยู่ต่ำกว่าตนเอง เช่น คน ยากจน หรือ สัตว์น้อยใหญ่”
เมตตาค้ำจุนโลก
Cr: คู่มือมนุษย์
-
 @ 58537364:705b4b85
2025-05-15 16:26:49
@ 58537364:705b4b85
2025-05-15 16:26:49ความสุขแท้ไม่มีในโลก มีแต่เมื่อความทุกข์ได้ถูกบำบัดลงครั้งหนึ่ง ก็เรียกว่าความสุขครั้งหนึ่ง คุณอยากได้ของสักชิ้นอย่างมาก เมื่อได้มาแล้วก็มีความสุข เพราะความอยากได้ถูกบำบัดไปแล้ว เมื่อคุณอยากได้ของหรืออยากได้อะไรอีก ความทุกข์ก็เกิดขึ้นอีก เมื่ออยากมาก ก็ทุกข์มาก เมื่อไม่อยากให้ของสิ่งนั้นหายหรือแตกดับไป ก็ทุกข์อีก
เมื่อได้รับของที่ต้องการแล้ว ก็ต้องดูแลเอาใจใส่ของนั้น เมื่อไม่เป็นไปตามความอยากหรือไม่อยากของตน ก็ทุกข์ ซึ่งทุกสรรพสิ่ง เมื่อเกิดขึ้น ย่อมตั้งอยู่แล้วดับไป คนที่เรารักย่อมเจ็บป่วยและดับไป เป็นธรรมดาของชีวิต แต่เราไม่ยอมรับ บางคนเมื่อพูดถึงความตาย ก็บอกว่า พูดทำไม เป็นคำอัปมงคล แต่โดยแท้แล้ว ความตายอยู่กับเราทุกลมหายใจ
เราต้องการให้คนรอบๆ ทำแต่สิ่งที่ถูกใจเรา ทำสิ่งที่ดีต่อเรา แต่มันจะเป็นไปได้หรือ ความสุขจึงอยู่ที่การยอมรับในสิ่งที่เป็น ที่มีอยู่ เพราะธรรมชาติของสิ่งที่เราต้องพบ ต้องประสบ มันเป็นเช่นนั้นของมันเอง การพยายามไปเปลี่ยนแปลงสิ่งต่างๆรอบๆตัว จึง เหมือนการพยายามห้ามแม่น้ำไม่ให้ไหลไป
ความสุขในฐานะปุถุชนมีได้ ด้วยการยอมรับสิ่งที่เกิดขึ้น การยอมรับไม่ใช่การยอมแพ้แก่มัน แต่เมื่อเราพยายามทำดีอย่างที่สุดแล้ว ผลสุดท้ายจะเป้นอย่างไร ก็ต้องวาง
ขอยกคำหลวงพ่อไพศาลที่ว่า ชีวิตเราเลือกได้ ว่าจะเป็นอย่างไร เด็กผู้หญิง 10 ขวบ ขนของ แต่เด็กผู้ชายสองคน ไม่ช่วยขนของ ไปดูทีวีเสีย แทนที่เด็กผู้หญิงคนนั้นจะโกรธ กลับบอกว่า ขนของเหนื่อยอย่างเดียว แต่ถ้าไปโกรธเขา เราก็เหนื่อยสองอย่าง
การอยู่โดยมองโลกในแง่บวก เป็นสิ่งที่สำคัญมาก ขอยกตัวอย่างจากหลวงพ่อไพศาลอีกครั้ง เด็กชายคนหนึ่งเป็นโรคมะเร็งที่ กระดูกที่ขา เขาถูกตัดขาไปข้างหนึ่ง เขาบอกว่า เขาดีใจที่ยังมีขาอีกข้างหนึ่ง ไม่ใช่เสียใจที่เสียขาไป
เป็นสุขในทุกความเปลี่ยนแปลง หลวงพ่อไพศาล วิสาโล
คนเราย่อมปรารถนาความเปลี่ยนแปลง หากว่าความเปลี่ยนแปลงนั้นอยู่ในอำนาจของเรา หรือสอดคล้องกับความต้องการของเรา ไม่มีใครอยากขับรถคันเดิม ใช้โทรศัพท์เครื่องเดิม หรืออยู่กับที่ไปตลอด มิจำต้องพูดถึงการอยู่ในอิริยาบถเดิม ๆ เราต้องการสิ่งใหม่ ๆ อยู่เสมอ แต่ความจริงอย่างหนึ่งที่เราปฏิเสธไม่ได้ก็คือ มีความเปลี่ยนแปลงหลายอย่างที่เราไม่ต้องการแต่หนีไม่พ้น ความเปลี่ยนแปลงอย่างนี้แหละที่ผู้คนประหวั่นพรั่นพรึง วิตกกังวลเมื่อนึกถึงมัน และเป็นทุกข์เมื่อมันมาถึง
แต่ยังมีความจริงอีกอย่างหนึ่งที่เราพึงตระหนักก็คือ สุขหรือทุกข์นั้น มิได้ขึ้นอยู่กับว่า มีอะไรเกิดขึ้นกับเรา แต่อยู่ที่ว่า เรารู้สึกอย่างไรกับสิ่งนั้นต่างหาก แม้มีสิ่งไม่ดีเกิดขึ้นกับเรา แต่ถ้าเราไม่รู้สึกย่ำแย่ไปกับมัน หรือวางใจให้เป็น มันก็ทำให้เราเป็นทุกข์ไม่ได้
กนกวรรณ ศิลป์สุข เป็นโรคธาลัสซีเมียตั้งแต่เกิด ทำให้เธอมีร่างกายแคระแกร็น กระดูกเปราะและเจ็บป่วยด้วยโรคแทรกซ้อนนานาชนิด ซึ่งมักทำให้อายุสั้น แต่เธอกับน้องสาวไม่มีสีหน้าอมทุกข์แต่อย่างใด กลับใช้ชีวิตอย่างมีความสุข เธอพูดจากประสบการณ์ของตัวเองว่า “มันไม่สำคัญหรอกว่าเราจะเป็นอย่างไรหรือมีอะไรเกิดขึ้นกับชีวิต แต่สำคัญที่ว่าเมื่อเกิดขึ้นมาแล้ว เราคิดกับมันยังไงต่างหาก สำหรับเราสองคน ความสุขเป็นเรื่องที่หาง่ายมาก ถ้าใจของเราคิดว่ามันเป็นความสุข”
โอโตทาเกะ ฮิโรทาดะ เกิดมาพิการ ไร้แขนไร้ขา แต่เขาสามารถช่วยตัวเองได้แทบทุกอย่าง ในหนังสือเรื่อง ไม่ครบห้า เขาพูดไว้ตอนหนึ่งว่า “ผมเกิดมาพิการแต่ผมมีความสุขและสนุกทุกวัน” ใครที่ได้รู้จักเขาคงยอมรับเต็มปากว่าเขาเป็นคนที่มีความสุขคนหนึ่ง อาจจะสุขมากกว่าคนที่มีอวัยวะครบ (แต่กลับเป็นทุกข์เพราะหน้ามีสิว ผิวตกกระ หุ่นไม่กระชับ)
ในโลกที่ซับซ้อนและผันผวนปรวนแปรอยู่เสมอ เราไม่สามารถเลือกได้ว่าจะต้องมีสิ่งดี ๆ เกิดขึ้นกับเราตลอดเวลา แต่เราเลือกได้ว่าจะมีปฏิกิริยากับสิ่งนั้นอย่างไร รวมทั้งเลือกได้ว่าจะยอมให้มันมีอิทธิพลต่อเราอย่างไรและแค่ไหน..ในวันที่แดดจ้าอากาศร้อนอ้าว บุรุษไปรษณีย์คนหนึ่งยืนรอส่งเอกสารหน้าบ้านหลังใหญ่ หลังจากเรียกหาเจ้าของบ้านแต่ไม่มีวี่แววว่าจะมีคนมารับ เขาก็ร้องเพลงไปพลาง ๆ เสียงดังชัดเจนไปทั้งซอย ในที่สุดเจ้าของบ้านก็ออกจากห้องแอร์มารับเอกสาร เธอมีสีหน้าหงุดหงิด เมื่อรับเอกสารเสร็จเธอก็ถามบุรุษไปรษณีย์ว่า “ร้อนแบบนี้ยังมีอารมณ์ร้องเพลงอีกเหรอ” เขายิ้มแล้วตอบว่า “ถ้าโลกร้อนแต่ใจเราเย็น มันก็เย็นครับ ร้องเพลงเป็นความสุขของผมอย่างหนึ่ง ส่งไปร้องไป” ว่าแล้วเขาก็ขับรถจากไป
เราสั่งให้อากาศเย็นตลอดเวลาไม่ได้ แต่เราเลือกได้ว่าจะยอมให้อากาศร้อนมีอิทธิพลต่อจิตใจของเราได้แค่ไหน นี้คือเสรีภาพอย่างหนึ่งที่เรามีกันทุกคน อยู่ที่ว่าเราจะใช้เสรีภาพชนิดนี้หรือไม่ พูดอีกอย่างก็คือ ถ้าเราหงุดหงิดเพราะอากาศร้อน นั่นแสดงว่าเราเลือกแล้วที่จะยอมให้มันยัดเยียดความทุกข์แก่ใจเรา
ถึงที่สุดแล้ว สุขหรือทุกข์อยู่ที่เราเลือก มิใช่มีใครมาทำให้ ถึงแม้จะป่วยด้วยโรคร้าย เราก็ยังสามารถมีความสุขได้ โจว ต้า กวน เด็กชายวัย ๑๐ ขวบ เป็นโรคมะเร็งที่ขา จนต้องผ่าตัดถึง ๓ ครั้ง เขาได้เขียนบทกวีเล่าถึงประสบการณ์ในครั้งนั้นว่า เมื่อพ่อแม่จูงมือเขาเข้าห้องผ่าตัด เขาเลือก “น้องสงบ” เป็นเพื่อน (แทนที่จะเป็น “น้องกังวล”) เมื่อเขาห้องผ่าตัดครั้งที่สอง เขาเลือก “ลุงมั่นคง”เป็นเพื่อน (แทนที่จะเป็น “ป้ากลัว”) เมื่อพ่ออุ้มเขาเข้าห้องผ่าตัดครั้งที่สาม เขาเลือก “ชีวิต” (แทนที่จะเป็น “ความตาย”) ด้วยการเลือกเช่นนี้มะเร็งจึงบั่นทอนได้แต่ร่างกายของเขา แต่ทำอะไรจิตใจเขาไม่ได้
เมื่อใดก็ตามที่ความเปลี่ยนแปลงอันไม่พึงประสงค์เกิดขึ้น หากเราไม่สามารถสกัดกั้นหรือบรรเทาลงได้ ในยามนั้นไม่มีอะไรดีกว่าการหันมาจัดการกับใจของเราเอง เพื่อให้เกิดความทุกข์น้อยที่สุด หรือใช้มันให้เกิดประโยชน์มากที่สุด ด้วยวิธีการต่อไปนี้
๑. ยอมรับความจริงที่เกิดขึ้นแล้ว การยอมรับความจริงที่ไม่พึงประสงค์ ทำให้เราเลิกบ่น ตีโพยตีพาย หรือมัวแต่ตีอกชกหัว ซึ่งมีแต่จะเพิ่มความทุกข์ให้แก่ตนเอง คนเรามักซ้ำเติมตัวเองด้วยการบ่นโวยวายในสิ่งที่ไม่อาจแก้ไขอะไรได้
เรามักทำใจยอมรับความจริงที่เกิดขึ้นแล้วไม่ได้ เพราะเห็นว่ามันไม่ถูกต้อง ไม่น่าเกิด ไม่ยุติธรรม (“ทำไมต้องเป็นฉัน ?”) แต่ยิ่งไปยึดติดหรือหมกมุ่นกับเหตุผลเหล่านั้น เราก็ยิ่งเป็นทุกข์ แทนที่จะเสียเวลาและพลังงานไปกับการบ่นโวยวาย ไม่ดีกว่าหรือหากเราจะเอาเวลาและพลังงานเหล่านั้นไปใช้ในการรับมือกับสิ่ง ที่เกิดขึ้นแล้ว
เด็ก ๓ คนได้รับมอบหมายให้ขนของขึ้นรถไฟ แต่ระหว่างที่กำลังขนของ เด็กชาย ๒ คนก็ผละไปดูโทรทัศน์ซึ่งกำลังถ่ายทอดสดการชกมวยของสมจิตร จงจอหอ นักชกเหรียญทองโอลิมปิค เมื่อมีคนถามเด็กหญิงซึ่งกำลังขนของอยู่คนเดียวว่า เธอไม่โกรธหรือคิดจะด่าว่าเพื่อน ๒ คนนั้นหรือ เธอตอบว่า “หนูขนของขึ้นรถไฟ หนูเหนื่อยอย่างเดียว แต่ถ้าหนูโกรธหรือไปด่าว่าเขา หนูก็ต้องเหนื่อยสองอย่าง”
ทุกครั้งที่ทำงาน เราสามารถเลือกได้ว่าจะเหนื่อยอย่างเดียว หรือเหนื่อยสองอย่าง คำถามคือทุกวันนี้เราเลือกเหนื่อยกี่อย่าง นอกจากเหนื่อยกายแล้ว เรายังเหนื่อยใจด้วยหรือไม่
การยอมรับความจริง ไม่ได้แปลว่ายอมจำนนต่อสิ่งที่เกิดขึ้น แต่เป็นจุดเริ่มต้นของการเลือกที่จะไม่ยอมทุกข์เพราะความเปลี่ยนแปลง อีกทั้งยังทำให้สามารถตั้งหลักหรือปรับตัวปรับใจพร้อมรับความเปลี่ยนแปลง นั้นอย่างดีที่สุด
๒. ทำปัจจุบันให้ดีที่สุด นอกจากบ่นโวยวายกับสิ่งที่เกิดขึ้นแล้ว เรามักทุกข์เพราะอาลัยอดีตอันงดงาม หรือกังวลกับสิ่งเลวร้ายที่คาดว่าจะเกิดขึ้นในอนาคต สุดท้ายก็เลยไม่เป็นอันทำอะไร
ไม่ว่าจะอาลัยอดีตหรือกังวลกับอนาคตเพียงใด ก็ไม่ช่วยให้อะไรดีขึ้น กลับทำให้เราย่ำแย่กว่าเดิม สิ่งเดียวที่จะทำให้อะไรดีขึ้นก็คือการทำปัจจุบันให้ดีที่สุด ทางข้างหน้าแม้จะยาวไกลและลำบากเพียงใด แต่เราไม่มีวันถึงจุดหมายเลยหากไม่ลงมือก้าวเสียแต่เดี๋ยวนี้ รวมทั้งใส่ใจกับแต่ละก้าวให้ดี ถ้าก้าวไม่หยุดในที่สุดก็ต้องถึงที่หมายเอง
บรู๊ซ เคอร์บี นักไต่เขา พูดไว้อย่างน่าสนใจว่า “ทุกอย่างมักจะดูเลวร้ายกว่าความจริงเสมอเมื่อเรามองจากที่ไกล ๆ เช่น หนทางขึ้นเขาดูน่ากลัว....บางเส้นทางอาจดูเลวร้ายจนคุณระย่อและอยากหันหลัง กลับ นานมาแล้วผมได้บทเรียนสำคัญคือ แทนที่จะมองขึ้นไปข้างบนและสูญเสียกำลังใจกับการจินตนาการถึงอันตรายข้าง หน้า ผมจับจ้องอยู่ที่พื้นใต้ฝ่าเท้าแล้วก้าวไปข้างหน้าทีละก้าว”
๓. มองแง่บวก มองแง่บวกไม่ได้หมายถึงการฝันหวานว่าอนาคตจะต้องดีแน่ แต่หมายถึงการมองเห็นสิ่งดี ๆ ที่มีอยู่ในปัจจุบัน ไม่ว่าเจ็บป่วย ตกงาน หรืออกหัก ก็ยังมีสิ่งดี ๆ อยู่รอบตัวและในตัวเรา รวมทั้งมองเห็นสิ่งดี ๆ ที่ซุกซ่อนอยู่ในความเปลี่ยนแปลงเหล่านั้นด้วย
แม้กนกวรรณ ศิลป์สุข จะป่วยด้วยโรคร้าย แต่เธอก็มีความสุขทุกวัน เพราะ “เราก็ยังมีตาเอาไว้มองสิ่งที่สวย ๆ มีจมูกไว้ดมกลิ่นหอม ๆ มีปากไว้กินอาหารอร่อย ๆ แล้วก็มีร่างกายที่ยังพอทำอะไรได้อีกหลายอย่าง แค่นี้ก็เพียงพอแล้วที่เราจะมีความสุข” ส่วนจารุวรรณ ศิลป์สุข น้องสาวของเธอ ซึ่งขาหักถึง ๑๔ ครั้งด้วยโรคเดียวกัน ก็พูดว่า “ขาหักก็ดีเหมือนกัน ไม่ต้องไปโรงเรียน ได้อยู่กับบ้าน ฟังยายเล่านิทาน หรือไม่ก็อ่านหนังสือ อยู่กับดอกไม้ กับธรรมชาติ กับสิ่งที่เราชอบ ก็ถือว่ามีความสุขไปอีกแบบ”
โจว ต้า กวน แม้จะถูกตัดขา แต่แทนที่จะเศร้าเสียใจกับขาที่ถูกตัด เขากลับรู้สึกดีที่ยังมีขาอีกข้างหนึ่ง ดังตั้งชื่อหนังสือรวมบทกวีของเขาว่า “ฉันยังมีขาอีกข้างหนึ่ง”
หลายคนพบว่าการที่เป็นมะเร็งทำให้ตนเองได้มาพบธรรมะและความสุขที่ลึกซึ้ง จึงอดไม่ได้ที่จะอุทานว่า “โชคดีที่เป็นมะเร็ง” ขณะที่บางคนบอกว่า “โชคดีที่เป็นแค่มะเร็งสมอง” เพราะหากเป็นมะเร็งปากมดลูกเธอจะต้องเจ็บปวดยิ่งกว่านี้
ถึงที่สุด ไม่ว่าอะไรเกิดขึ้นกับเรา ก็ล้วนดีเสมอ อย่างน้อยก็ดีที่ไม่แย่ไปกว่านี้
๔. มีสติ รู้เท่าทันตนเอง เมื่อความเปลี่ยนแปลงที่ไม่พึงประสงค์เกิดขึ้น เรามักมองออกนอกตัว และอดไม่ได้ที่จะโทษคนโน้น ต่อว่าคนนี้ และเรียกหาใครต่อใครมาช่วย แต่เรามักลืมดูใจตนเอง ว่ากำลังปล่อยให้ความโกรธแค้น ความกังวล และความท้อแท้ครอบงำใจไปแล้วมากน้อยเพียงใด เราลืมไปว่าเป็นตัวเราเองต่างหากที่ยอมให้เหตุการณ์ต่าง ๆ รอบตัวยัดเยียดความทุกข์ให้แก่ใจเรา ไม่ใช่เราดอกหรือที่เลือกทุกข์มากกว่าสุข การมีสติ ระลึกรู้ใจที่กำลังจมอยู่กับความทุกข์ จะช่วยพาใจกลับสู่ความปกติ เห็นอารมณ์ต่าง ๆ เกิดขึ้นโดยไม่ไปข้องเกี่ยว จ่อมจม หรือยึดติดถือมั่นมัน อีกทั้งยังเปิดช่องและบ่มเพาะปัญญาให้ทำงานได้เต็มที่ สามารถเปลี่ยนร้ายให้กลายเป็นดี หรือมองเห็นด้านดีของมันได้
สติและปัญญาทำให้เรามีเสรีภาพที่จะเลือกสุข และหันหลังให้กับความทุกข์ ใช่หรือไม่ว่าอิสรภาพที่แท้ คือ ความสามารถในการอนุญาตให้สิ่งต่าง ๆ มีอิทธิพลต่อชีวิตของเราได้เพียงใด ความเปลี่ยนแปลงของร่างกาย ของทรัพย์สิน ของผู้คนรอบตัว รวมทั้งความเปลี่ยนแปลงในบ้านเมือง ไม่สามารถทำให้เราทุกข์ได้ หากเราเข้าถึงอิสรภาพดังกล่าว แทนที่เราจะมัววิงวอนเรียกร้องให้เกิดความเปลี่ยนแปลงที่ถูกใจเรา ไม่ดีกว่าหรือหากเราพยายามพัฒนาตนบ่มเพาะจิตใจให้เข้าถึงอิสรภาพดังกล่าว ควบคู่ไปกับการสร้างสรรค์สิ่งดีงามให้เกิดขึ้นแก่ตนเองและสังคม
credit : Suphan Click!!
-
 @ 0b118e40:4edc09cb
2025-05-15 15:40:21
@ 0b118e40:4edc09cb
2025-05-15 15:40:21My week started off with a lovely message from a friend : “I often think about you. Especially during times when it requires me to be more resilient and have faith in myself. I always carry your note in the book you gave me, “what the dog saw” And it always gives me courage and I send a little prayer your way”.
This friend of mine was dealing with the undercurrent of discrimination in my alma mater when we first met, and I helped out. It's something anybody would have done, but surprisingly, nobody else showed up. We’ve stayed in touch over the years, and my friend went on to help a lot of other people along the way.
I don’t remember what I wrote in that note. It’s something I tend to do (write notes, give books, write notes in books). But the message boomeranged back to me at a time when I needed to hold the line. To keep the faith.
Most of us don’t talk about our struggles. And sometimes the smallest act, which could just be a kind word or a reminder of the person you are, can carry farther than we imagine.
On the act of giving
There’s a book called Give and Take by Adam Grant. I picked it up hoping to learn how to take, because it’s always been easier to give and harder to accept help. But what I learned was something else entirely.
Grant studied over 30,000 people across different companies and grouped them into three types: * Givers * Matchers * Takers
Based on his studies, givers often finish last... They struggle the most. They burn out. They get overlooked. They’re too trusting.
But oddly, they also rise to the very top.
Matchers are the scorekeepers, the “I’ll help you if you help me” kind. They make up most of the population. The fascinating thing about tit-for-tat is that if someone’s kind, they reciprocate. But if someone acts like a jerk, they return the energy, and over time, it becomes a pool of spoiled milk. Matchers are a lukewarm, forgettable kind of network.
Takers are the ones chasing attention, always aligning themselves with whoever looks powerful. They tend to float toward status and soak up what they can. But they often portray themselves as kind and giving.
One example Grant shared was Enron's Kenneth Lay, who was at the center of one of the biggest corporate scandals in U.S. history. He hung around wherever he’d get seen or validated. He funded both Bush and Clinton, hedging his bets on who might win by securing proximity. Sadly, when Enron crumbled, he died of a heart attack before his prison sentencing.
Most people steer clear from takers because they are just exhausting. And takers often collapse under the weight of their own games.
But takers aren’t the lowest performers. That spot belongs to a certain kind of giver—the self-neglecting kind. The ones with no boundaries, no clarity, and no self-awareness. They give in to avoid conflict, to feel worthy, or because they don’t know how to say no. And when life breaks them, they point fingers.
Then there’s the other kind of giver. The ones who build trust and build people up without asking for a receipt.
These givers: 1. Give without expectation, from a place of purpose 2. Build and uplift others without seeking credit 3. Set boundaries and walk away when giving turns into draining
This group of givers rarely talk much about what they do for others. But when you hear about it or see it, it stays with you. It makes you want to show up a little better.
Why open source environments feels like home
The more I thought about it, the more I saw how deeply open source reflects that kind of giving that ends up right at the top.
In open source, you don’t last if it’s just about ego. You can’t fake it. There are no titles, no awards. You either show up to build and help, or you don’t.
People who give without needing to be seen are the ones the community leans on. You can tell when someone’s pretending to care. It’s in their tone, their urgency and their sense of transaction. The genuine ones don’t need to brand themselves as generous. They just are.
Open source works because giving is the default setting. The work speaks volumes and generosity compounds. The system filters for people who show up with purpose and stay consistent.
It’s also why the ones who whine, posture, or manipulate rarely last. They might call themselves givers, but they’re not fooling anyone who’s actually doing the work.
Adam Grant found that for giver cultures to thrive, takers have to be removed. They need to be pruned. Because takers poison the well. They drain givers, shift the culture from contribution to calculation, and unravel the trust that holds open systems together.
When hope boomerangs
That note is something I don’t remember writing. But it found its way back to me, and it was a good reminder to take my own advice and keep the faith.
And maybe that’s the point.
You do a small thing. And years later, it circles back when it matters most. Not because you expected it. But because you mattered.
According to Grant, givers do best when they combine generosity with grit and strategy. They create networks built on goodwill, which eventually open doors others don’t even know exist.
So if you’re wondering where I’m going with this, do something genuinely kind for someone today. Even if it’s as simple as sending a kind note. Not for you to be seen or heard. And not for you to keep scores.
But, just because.
-
 @ 04c915da:3dfbecc9
2025-05-15 15:31:45
@ 04c915da:3dfbecc9
2025-05-15 15:31:45Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ c1e6505c:02b3157e
2025-05-15 15:25:27
@ c1e6505c:02b3157e
2025-05-15 15:25:27“Put that camera down, you bitch,” someone yelled out of a car as it drove by with the door wide open.

I had a little time in Savannah yesterday to walk around and take some photos. I tend to wander through the rougher areas — not just in Savannah, but in any city I visit. I’m drawn to the spots most people avoid. Not the tourist zones, but the alleys, the quiet, broken-down neighborhoods where the grit is.
I’ve photographed Savannah a lot over the past few years, so it’s getting harder to find places I haven’t already been. But every now and then, I’ll stumble on a back street or alley I’ve never seen before, and in it, something I’m almost certain no one else has photographed.
There’s something about walking aimlessly with a camera that I find incredibly fulfilling. Honestly, if I could do just that for the rest of my life — wander around and photograph things that most people overlook — I’d be content.

There’s a quote I heard recently - can’t remember who said it — but it stuck with me. It was something like: “It’s better to be aimless than to be rigid with a plan.” Because when you’re too locked into a goal, you might miss the opportunities that pop up along the way. You need to stay flexible, fluid—open to what the world hands you.
That’s how I feel about photography. I’ll walk for hours—sometimes five to ten miles — just to see what shows up. It becomes a game. A game between me, the camera, the street, and whatever decides to show up that day.
Usually, it takes a few warm-up shots to get into it — just pictures of objects, whatever catches my eye. But once I find a rhythm, it’s like the world starts to reveal itself. The good stuff comes out of hiding.
That’s what real photography is to me. Not staging scenes or setting up portraits—that’s more like illustration, as Garry Winogrand would say. What I care about is life. Life unfolding right in front of you. Life happening.









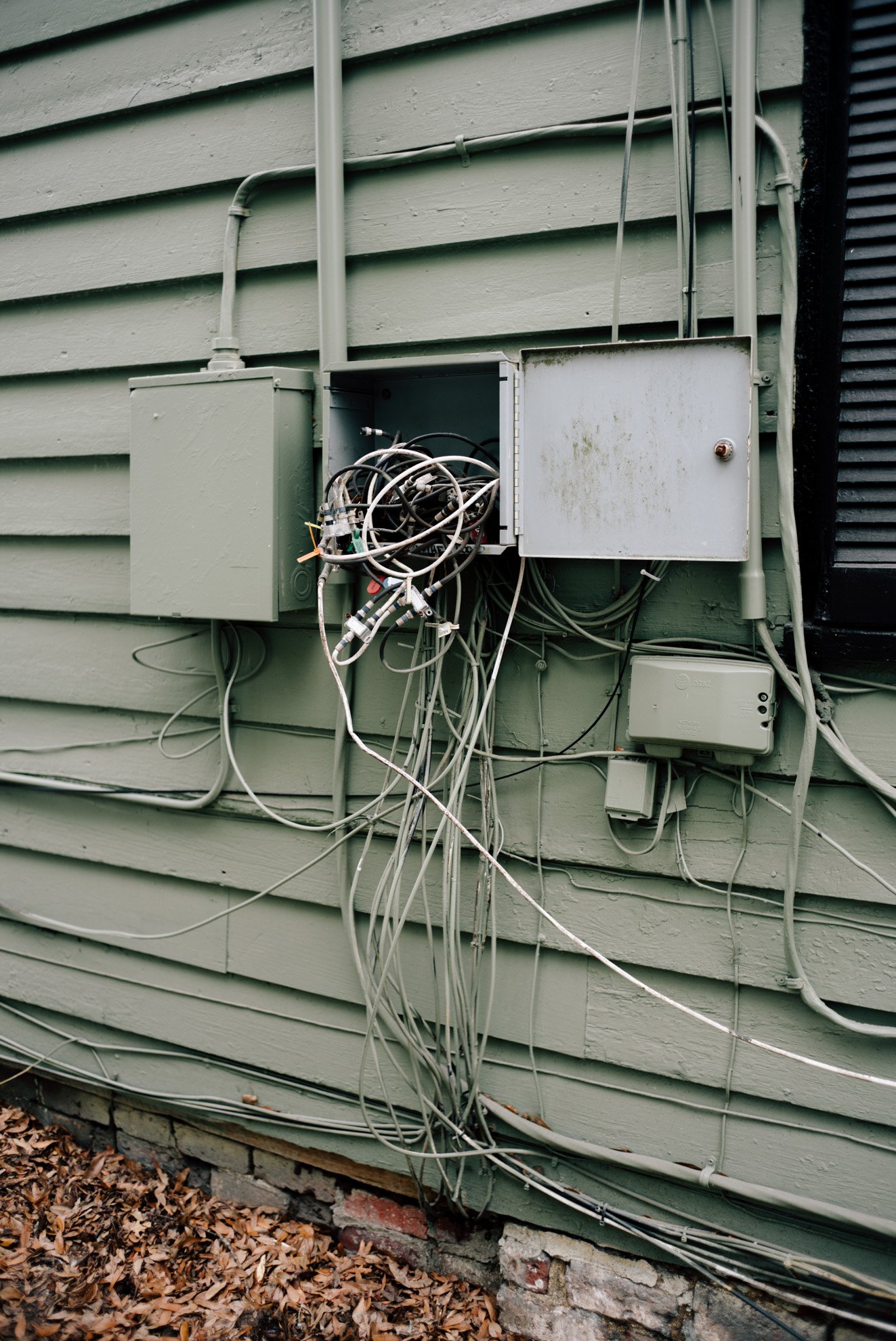





Thank you for your attention. Please consider donating a few sats if you enjoy my work. It goes a long way. If not, please share. Thank you.
-
 @ a296b972:e5a7a2e8
2025-05-15 15:07:57
@ a296b972:e5a7a2e8
2025-05-15 15:07:57***Unserestaatsanwaltschaft***
Die Staatsanwaltschaft Aachen prüft Ermittlungen gegen Unbekannt in Sachen Cum-Ex. Hierfür konnte die ehemalige Chefanklägerin Brohilker als externe Expertin gewonnen werden. Korrektur, die Staatsanwaltschaft prüft Ermittlungen gegen Frau Brohilker. „Richtig so“, sagen Experten. „Es sind doch nur 43 Milliarden im Bermuda-Dreieck verschollen. Man muss auch mal Ruhe geben, genauso, wie bei Corona“. Dank schon heute an Unserestaatsanwaltschaft.
***Bundesamt für Fassungslosigkeit***
Ein Enkel hat die Kochrezepte seiner Großmutter zusammengetragen und veröffentlicht. Ausschließlich Rezepte aus Ostpreußen, Pommern und Schlesien. Das gesamte Kochbuch ist jetzt als Nazi-Küche eingestuft worden, weil der Urenkel die Grenze des guten Geschmacks, also die Oder-Neisse-Linie, dadurch missachtet hat. Weiter wurde ihm Russenfreundlichkeit vorgeworfen, weil auch ein Rezept für Königsberger Klopse abgedruckt wurde.
***Stillhaltezusage***
Die vom Bundesamt für Verfassungsschutz ausgesprochene Stillhaltezusage hat Zahnärzte auf die Idee gebracht, diese vor Behandlung von ihren Patienten unterschreiben zu lassen. Widerstand ist zwecklos.
***Paragraphenerweiterung***
Das Würgen des Menschen ist unfassbar. Jeder, der sich dafür einsetzt, dass wieder die Vernunft in Deutschland Einzug hält, wird mit einem Urlaub mit dem Corona-Minister II nicht unter 6 Wochen bestraft.
***Freie Kapazitäten beim Verfassungsschutz***
Das als gesichert stillgehaltene Gutachten hat gezeigt, dass das Bundesamt über erhebliche Kapazitäten verfügt. Diese sollen jetzt gebündelt dazu verwendet werden, die Messerattentate und den Tatbestand der selbstfahrenden Autos in Menschenmengen lückenlos aufzuklären. Erfahrung bei dem Zusammentragen von öffentlichen Zitaten verspricht nun endlich eine zeitnahe Aufklärung.
***Sonderdezernat beim schutzverfassenden Bundesamt***
Die Sprengung der Nordstream 2-Pipeline war ein terroristischer Anschlag auf die Energieversorgung von Deutschland und ganz Europa. Zur nun endgültigen Aufklärung nach nur wenigen Jahren wurde ein Sonderdezernat mit dem Code-Namen „Task Force Peng“ eingerichtet. Man hat bereits Kontakt zu Seymour Hersh aufgenommen, doch der ist zurzeit mit einem Segelboot namens „Andromeda“ auf Weltumrundung unterwegs.
***Eurovision Song Contest***
Der ESC ist eine absolut politisch neutrale Sing-Veranstaltung, bei der persönliche Angriffe gegen Repräsentanten und Innen stets im Bereich des Unmöglichen bleiben. Auch solidarische Gewinnerermittlung zur Unterstützung eines bestimmten Landes entbehrt jeder Grundlage, wie die Vergangenheit wiederholt gezeigt hat.
***Drehtüreffekt***
Das Infragestellen von Personen, die von der Politik in die Medien oder umgekehrt wechseln, hat nichts mit Interessenkonflikten zu tun. Im Gegenteil: Es werden so Kompetenzen ressourcenschonend anschlussverwendet.
***‘Aufrüstung in Deutschland***
Nachdem man zunächst einen Feind erfunden hat, der keine Lust hat, einer zu sein, ist die zwingend logische Schlussfolgerung daraus, dass man jetzt auch wieder die zentrale Macht in Europa werden will. Das freut die Nachbarn, und wie schon in der Ukraine in 2022, beginnt die neue deutsche Zeitrechnung jetzt in 2025. Man ist zu der Überzeugung gelangt, dass Vorgeschichten von Nationen völlig überbewertet werden.
***Vergleich unzulässig***
Die geplante Zerschlagung des Kapitalismus durch die Linke ist etwas völlig anderes, als die Bekämpfung des Kapitalismus zugunsten des Sozialismus durch die SED, weil es damals um die Deutsche Mark ging und heute schließlich um den Euro.
***Bevorstehende Hitzewelle Sommer 2025***
Nach den vergeblichen zwei Anläufen durch plötzlich und unerwarteten Regen in den Jahren 2023 und 2024 ist man sich nun ganz sicher, dass die Erdverkochung durch die Klimawandelung im dritten Anlauf stattfinden wird. Es wurden schon Bodentemperaturen gemessen.
***Neueintrag im Knigge***
Ab sofort schickt es sich nicht, dass vollgeschnaufte Taschentücher auf dem Tisch liegengelassen werden dürfen, wenn die Kamera angeht. Auch Kratzlöffel, wenn der Rücken mal juckt, sind vor Einschalten der Kamera zu entfernen.
***Meinungsfreiheit***
Jeder darf die ihm von den Weisen der Wahrheit vorgegebene Meinung so oft wiederholen und aussprechen, wie er will. Eine Limitierung der Wiederholungen findet nicht statt.
***Selbstbestimmungsgesetz erweitert***
Das Selbstbestimmungsgesetz wurde jetzt erweitert: Man darf sich auch als Finanzamt definieren. Das hat den Vorteil, dass sich der Steuerpflichtige seine Steuerzahlungen auf sein eigenes Konto überweisen kann, um selbst zu entscheiden, wofür die Gelder der Allgemeinheit dienend, ausgegeben werden sollen.
***US-Verbot von Gain-of-Function Forschung***
Dafür, dass deutsche Unternehmen aufgrund der unbezahlbaren Energiekosten ihre Produktionsstätten ins Ausland verlagern, werden in deutschen Bio-Laboren die freigesetzten US-Kapazitäten aus der Forschung mit Kusshand aufgenommen. Operation Paperclip II, nur umgekehrt.
***Deutscher Weltrekord***
Noch nie wurden Ankündigungen in einem Koalitionsvertrag so schnell entsorgt, wie nach den Anfang Mai 2025 stattgefundenen Wahlen. Der verbleibende Rest sind Kann-Bestimmungen, für die sicher ein Grund gefunden wird, warum das Geld zur Umsetzung fehlt.
Dieser Artikel wurde mit dem Pareto-Client geschrieben
* *
(Bild von pixabay)
-
 @ a5ee4475:2ca75401
2025-05-15 14:44:45
@ a5ee4475:2ca75401
2025-05-15 14:44:45lista #descentralismo #compilado #portugues
*Algumas destas listas ainda estão sendo trocadas, portanto as versões mais recentes delas só estão visíveis no Amethyst por causa da ferramenta de edição.
Clients do Nostr e Outras Coisas
nostr:naddr1qq245dz5tqe8w46swpphgmr4f3047s6629t45qg4waehxw309aex2mrp0yhxgctdw4eju6t09upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4guxde6sl
Modelos de IA e Ferramentas
nostr:naddr1qq24xwtyt9v5wjzefe6523j32dy5ga65gagkjqgswaehxw309ahx7um5wghx6mmd9upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4guk62czu
Iniciativas de Bitcoin
nostr:naddr1qvzqqqr4gupzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqq2nvmn5va9x2nrxfd2k5smyf3ux7vesd9znyqxygt4
Profissionais Brasileiros no Nostr
nostr:naddr1qq24qmnkwe6y67zlxgc4sumrxpxxce3kf9fn2qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7q3q5hhygatg5gmjyfkkguqn54f9r6k8m5m6ksyqffgjrf3uut982sqsxpqqqp65wp8uedu
Comunidades em Português no Nostr
nostr:naddr1qq2hwcejv4ykgdf3v9gxykrxfdqk753jxcc4gqg4waehxw309aex2mrp0yhxgctdw4eju6t09upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4gu455fm3
Grupos em Português no Nostr
nostr:nevent1qqs98kldepjmlxngupsyth40n0h5lw7z5ut5w4scvh27alc0w86tevcpzpmhxue69uhkummnw3ezumt0d5hsygy7fff8g6l23gp5uqtuyqwkqvucx6mhe7r9h7v6wyzzj0v6lrztcspsgqqqqqqs3ndneh
Jogos de Código Aberto
Open Source Games nostr:naddr1qvzqqqr4gupzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqq2kvwp3v4hhvk2sw3j5sm6h23g5wkz5ddzhz8x40v0
Itens Úteis com Esquemas Disponíveis
nostr:naddr1qqgrqvp5vd3kycejxask2efcv4jr2qgswaehxw309ahx7um5wghx6mmd9upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4guc43v6c
Formatação de Texto em Markdown
(Amethyst, Yakihone e outros) nostr:naddr1qvzqqqr4gupzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqq2454m8dfzn26z4f34kvu6fw4rysnrjxfm42wfpe90
Outros Links
nostr:nevent1qqsrm6ywny5r7ajakpppp0lt525n0s33x6tyn6pz0n8ws8k2tqpqracpzpmhxue69uhkummnw3ezumt0d5hsygp6e5ns0nv3dun430jky25y4pku6ylz68rz6zs7khv29q6rj5peespsgqqqqqqsmfwa78
-
 @ f1989a96:bcaaf2c1
2025-05-15 14:42:29
@ f1989a96:bcaaf2c1
2025-05-15 14:42:29Good morning, readers!
We bring news from the Democratic Republic of Congo (DRC), where the Rwanda-backed M23 rebel group is imposing immense taxes on the local economy, merchants, and aid groups to fund its insurgency as it seeks to govern seized regions of the Eastern Congo. The levies worsen economic hardship for Congolese already suffering from ongoing cash shortages, bank closures, and rapidly rising prices induced by the regional conflict.
Meanwhile, in Hong Kong, independent media outlet Channel C, founded by former Apple Daily employees, had its bank account frozen by local officials over alleged fraud charges. The closure fits into a widespread pattern of the Chinese Communist Party (CCP) leveraging financial repression and legal pressure to silence independent and pro-democracy media in Hong Kong.
In freedom tech news, we highlight a new ecash development: multinut payments. These payments let users combine small balances held at different ecash mints to pay a single invoice. It’s a big step forward in terms of usability and security for human rights defenders since they no longer need to keep a large balance of ecash at any one mint. This reduces the chances of stolen funds while maintaining strong privacy guarantees. We also highlight the ongoing OP_RETURN debate in the Bitcoin community, present both sides of the argument, and invite our readers to watch a nuanced debate on this topic.
We end with the latest edition of the HRF x Pubkey Freedom Tech series, where the Human Rights Foundation’s Alex Gladstein discusses the upcoming Oslo Freedom Forum and HRF’s role in supporting open-source freedom tech with Pubkey’s co-founder, Thomas Pacchia. We also include the livestreams from the latest bitcoin++ event, where developers, privacy advocates, and freedom tech users convened to discuss Bitcoin’s mempool, learn how Bitcoin transactions are sorted into blocks, and discuss current mempool policies.
Now, let’s jump right in!
SUBSCRIBE HERE
GLOBAL NEWS
DR Congo | Rebel Rule and Economic Ruin
After seizing control of large parts of the eastern Congo, the Paul Kagame-backed M23 rebel group is now trying to govern and fund its insurgency through coercive taxation and financial control. Rebels now impose a 15% tax on coltan metal production, 20% duties on merchants selling essential goods, and demand tax bills from aid groups, backed by threats of physical punishment. “If you don’t pay up, you risk being whipped,” one merchant said. The new levies are worsening the financial struggles for Congolese already suffering from ongoing cash shortages, bank closures, and rapidly rising prices induced by the regional conflict. Many must travel hundreds of kilometers just to obtain cash while navigating the backdrop of a humanitarian crisis that has claimed more than 7,000 lives.
China | Law Enforcement Freezes Bank Accounts of Independent Media Outlet Channel C
Hong Kong-based Channel C, an independent media outlet founded by former Apple Daily employees, reports that its bank accounts are frozen, forcing the news outlet to halt operations. Local law enforcement claim the outlet abused a COVID-era loan scheme and arrested one of its directors for alleged fraud. Still, the closure fits a well-worn pattern: using financial and legal repression to silence independent media in Hong Kong. Pro-democracy newspaper Apple Daily faced a nearly identical fate in 2021 when its assets were seized and its founder, Jimmy Lai, was imprisoned under Hong Kong’s new national security law. Lai now faces up to life in prison. When access to money becomes contingent on political obedience, press freedom can’t survive.
Venezuela | Blackouts, Inflation, and Currency Shortages
Venezuelans are once again bracing for economic collapse as inflation rises to 162% and electrical blackouts sweep across major cities. The situation echoes 2019’s political and financial chaos, where triple-digit inflation, foreign currency shortages, and power outages paralyzed the country. In reaction to the collapse, Nicolás Maduro approved the country’s first economic emergency decree in four years, granting himself broad powers to suspend taxes and authorize new benefits for select investors. The regime has also reshuffled central bank leadership and is pressing merchants to abandon US dollar pricing and return to the failing bolivar system — a clear move to financially asphyxiate Venezuelans. A focus on top-down economic management by Maduro’s regime will only reinforce the inflation and poverty driving this widespread crisis in the wake of Maduro’s stolen and blatantly rigged presidential election.
Bolivia | Inflation Accelerates to 17-Year High
Inflation in Bolivia is accelerating rapidly, with prices rising more than 15% year over year. This is the highest level of inflation Bolivians have seen in 17 years. Families now face increased costs of essential goods like food, shelter, and water. And the country’s fixed exchange rate system is also faltering, with dwindling reserves and growing dollar shortages compounding the price increases. The Bolivian regime also approved a new decree to regulate financial technology companies and virtual asset providers. The regulations tighten control over platforms that offer alternatives to the depreciating boliviano. If implemented rigidly, these regulations could restrict access to tools like Bitcoin.
Nicaragua | Ortega Centralizes Passport Renewal in Managua for Exiled Dissidents
The regime of Daniel Ortega has stripped Nicaraguans abroad of a basic right: the ability to renew their passports at local embassies abroad. All renewals must now go through the Nicaraguan capital of Managua, forcing exiles to either return home or authorize a relative (via an apostilled power of attorney) to handle the renewal on their behalf. For many outside Nicaragua, especially political opposition, journalists, and human rights defenders, returning is not a safe option, and involving relatives could expose them to state repression or retaliation. Those who do return risk facing the immense physical and financial repression of the Ortega regime, including surveillance, extortion, bank freezes, or even imprisonment. Ortega’s corruption of even basic bureaucracy undermines the growing Nicaraguan diaspora’s ability to live freely abroad by making their legal status, mobility, and access to financial services conditional.
Kenya | High Court Rules Against Sam Altman and Worldcoin
A Kenyan High Court ruled that Worldcoin, the biometric ID project co-founded by Sam Altman, CEO of OpenAI, violated constitutional privacy rights by collecting iris scans and facial images without proper safeguards. The court ordered the immediate deletion of all biometric data collected from Kenyan users, including iris scans and facial images. They also banned the project from conducting any further data collection. Kenya had been one of Worldcoin’s largest markets before authorities suspended the project in 2023. As biometric surveillance becomes more widespread, this case highlights the risks of technologies that undermine privacy in the name of inclusion.
BITCOIN AND FREEDOM TECH NEWS
Cashu | Make Ecash Payments from Multiple Mints
Cashu, a protocol for making private bitcoin payments using ecash, shared a new feature called multinut payments. Still in development, it enables users to combine small ecash balances held at different mints (entities that issue and redeem ecash) into a single transaction. Since Cashu is a custodial system (meaning users must trust the mints they use), this update reduces counterparty risk by allowing users to spread their funds across multiple mints rather than relying on just one. Previously, making a large ecash payment required keeping a sizeable balance at a single mint, increasing the chances of losing your funds if the mint were shut down or compromised. Now, larger payments can be made with significantly less custody risk. For those living under strict financial controls, ecash multinut payments offer a very private way to spend funds without trusting any single entity that can censor or debank them.
Bitika | Bridging Bitcoin and M-Pesa in Kenya
Bitika is a Kenyan fintech startup simplifying Bitcoin access. It integrates with M-Pesa, the mobile money platform used daily for payments by millions of people across Kenya and wider East Africa. Bitika offers a three-step process to buy Bitcoin via mobile phone using the Lightning Network. Users simply enter the amount of Bitcoin they would like to receive in Kenyan shillings, input their Bitcoin Lightning wallet address, and enter their M-Pesa number, and once confirmed, they receive their Bitcoin. Bitika is similar to other Bitcoin projects like Tando, which also bridges Bitcoin with M-Pesa using the Lightning Network. With plans to expand across the rest of Africa, Bitika shows Bitcoin’s grassroots utility and the role of local context in driving bottom-up financial inclusion. Try it here.
Frostsnap | New Bitcoin Multisig Custody Solution
Frostsnap is a new Bitcoin custody solution that uses a simplified multisignature setup to protect users' funds from theft, loss, or coercion by corrupt and authoritarian regimes. Rather than generating and storing private keys on a single device, multisignature solutions like Frostsnap employ multiple private keys distributed across different devices and locations. This approach eliminates single points of failure and offers strong resistance to physical attacks, device compromise, and forced access to users’ Bitcoin (such as from Chinese law enforcement, who surveil mail and extort Bitcoin). Frostsnap also offers the ability to spend directly from the multisig wallet, hide the wallet in times of duress, and access inheritance features, all critical functionalities for human rights defenders and nonprofits facing surveillance or financial repression. Learn more here.
OP_RETURN | Debate Over Bitcoin Core’s Data Relay Limits
A heated debate has resurfaced between some Bitcoin users and developers over whether to raise the size limit for OP_RETURN data that Bitcoin Core nodes (computers running Bitcoin’s main software implementation) relay. The debate was sparked when developer Peter Todd proposed removing this data limit from mempool policy on the basis that it could reduce reliance on direct miner connections, improve fee estimation, and shrink the Unspent Transaction Output (UTXO) set. It would do this by encouraging users to store arbitrary data in prunable, unspendable outputs (rather than spendable, persistent UTXOs). On the other hand, critics warn that lifting the OP_RETURN limit could increase spam, undermine Bitcoin’s focus on serving financial transactions, and weaken its censorship resistance. The debate still continues, but at its core, the disagreement highlights deeper tensions over what kinds of data should flow through the Bitcoin network. Tune into this discussion at the latest bitcoin++ developer conference to understand the nuance on both sides of the OP_RETURN debate.
Wasabi Wallet | Major Privacy Upgrade and Serverless Operation
Wasabi Wallet, a non-custodial, privacy-focused Bitcoin wallet, introduced its Prometheus update, which enables the wallet to synchronize and operate without a central server and increases transaction privacy. Users can now connect Wasabi directly to their own Bitcoin node (computer running the Bitcoin software), removing reliance on third-party infrastructure and reducing the risk of censorship. The update also introduces Coinjoin 2.0, a privacy technique that mixes the inputs of a Bitcoin transaction, in doing so protecting, for example, the identity of a dissident or nonprofit. Coinjoin 2.0 brings a redesigned mixing process that continuously registers coins as they become available. This change improves privacy and strengthens resistance to analysis that dictators can use to track payments.
Cove Wallet | Adds Support for Krux
Cove Wallet, an open-source mobile Bitcoin wallet currently in beta, released v0.4.0, which brings support for Krux hardware wallets. Krux is an open-source software and HRF grantee that turns generic computing devices into hardware wallets for secure Bitcoin self-custody and transactions. It can help decentralize access to Bitcoin and protect freedom and property rights in authoritarian regimes by providing a discrete and modular self-custody solution. By incorporating Krux, Cove offers its users a private, borderless, DIY path to financial sovereignty with no brand-name hardware. Cove Wallet also announced future support for coin control, which will grant users granular control over the specific coins they use in their Bitcoin payments and the ability to improve transaction privacy.
RECOMMENDED CONTENT
HRF x Pubkey — Freedom Tech and the Oslo Freedom Forum with Alex Gladstein
The latest edition of the HRF x Pubkey Freedom Tech series features a fireside chat with Alex Gladstein, chief strategy officer of HRF, in conversation with Pubkey co-founder Tom Pacchia. The discussion explores HRF’s role in funding and supporting open-source Freedom Tech, the upcoming Oslo Freedom Forum and the Freedom Tech track, as well as the human rights paradox of nation-state Bitcoin adoption. Catch the full conversation here.
bitcoin++ Developer Conference Livestream
Last week, bitcoin++ hosted the “mempool edition” of its Bitcoin developer conference series in Austin, Texas. The event, supported by HRF, brought together Bitcoin developers and freedom tech advocates for multiple days of hands-on development, workshops, and technical discussions surrounding Bitcoin’s mempool (the queue of pending transactions in a Bitcoin node). If you’d like to dive into the technical intricacies, you can catch the key sessions and workshops via live stream. Watch them here.
If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report here.
Support the newsletter by donating bitcoin to HRF’s Financial Freedom program via BTCPay.\ Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ hrf.org
The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals here.
-
 @ eb0157af:77ab6c55
2025-05-15 14:41:18
@ eb0157af:77ab6c55
2025-05-15 14:41:18Coinbase has revealed an attack in which a group of hackers bribed support agents to access user data.
Coinbase is facing a serious security crisis after a data breach on May 11. A hacker group claimed to have stolen sensitive customer information and demanded a $20 million ransom in bitcoin, threatening to release the data if the payment is not made.
In response, Coinbase CEO Brian Armstrong stated the company will not negotiate with criminals. Instead, the firm launched a countermeasure: a $20 million bounty for anyone who provides information leading to the identification and capture of the attackers.
In a post, the company added it will “reimburse customers who were tricked into sending funds to the attacker.”
Reports indicate the hackers managed to corrupt some Coinbase customer service agents, gaining access to the company’s internal systems. Once inside, they collected sensitive user data, including names, phone numbers, email addresses, and partial social security numbers. Masked bank details, ID document images, and snapshots of account balances were also compromised.

Coinbase confirmed the breach and said it acted swiftly to isolate affected systems and notify impacted users. Previous reports said the incident affected 1% of monthly transacting users.
The post Coinbase user data breached: hackers demand $20 million appeared first on Atlas21.
-
 @ a5ee4475:2ca75401
2025-05-15 14:11:16
@ a5ee4475:2ca75401
2025-05-15 14:11:16lists #descentralismo #compilation #english
*The last list was updated in Amethyst, so the update of this one will only be visible in Amethyst.
nostr:naddr1qq245dz5tqe8w46swpphgmr4f3047s6629t45qg4waehxw309aex2mrp0yhxgctdw4eju6t09upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4guxde6sl
AI
nostr:naddr1qq24xwtyt9v5wjzefe6523j32dy5ga65gagkjqgawaehxw309ahx7um5wghxy6t5vdhkjmn9wgh8xmmrd9skctczyzj7u3r4dz3rwg3x6erszwj4y502clwn026qsp99zgdx8n3v5a2qzqcyqqq823c8mw5zk
FOSS GAME
nostr:naddr1qq2kvwp3v4hhvk2sw3j5sm6h23g5wkz5ddzhzqg4waehxw309aex2mrp0yhxgctdw4eju6t09upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4gut57qtr
OSHW - Open Source Hardware
nostr:naddr1qqgrqvp5vd3kycejxask2efcv4jr2qgswaehxw309ahx7um5wghx6mmd9upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4guc43v6c
Markdown Uses for Some Clients
nostr:nevent1qqsv54qfgtme38r2tl9v6ghwfj09gdjukealstkzc77mwujr56tgfwsppemhxue69uhkummn9ekx7mp0qgsq37tg2603tu0cqdrxs30e2n5t8p87uenf4fvfepdcvr7nllje5zgrqsqqqqqpkdvta4
Other Links
nostr:nevent1qqsrm6ywny5r7ajakpppp0lt525n0s33x6tyn6pz0n8ws8k2tqpqracpzpmhxue69uhkummnw3ezumt0d5hsygp6e5ns0nv3dun430jky25y4pku6ylz68rz6zs7khv29q6rj5peespsgqqqqqqsmfwa78
-
 @ 8173f6e1:e488ac0f
2025-05-15 13:11:46
@ 8173f6e1:e488ac0f
2025-05-15 13:11:46TESTNOTEBIN2
-
 @ efe5d120:1fc51981
2025-05-15 12:53:31
@ efe5d120:1fc51981
2025-05-15 12:53:31It’s not big government programs or powerful institutions that make a society strong. It’s something much simpler: everyday people trading and working together.
Think about the local hardware store owner. He helps his neighbors, gives people jobs, and provides useful tools. But when the government taxes him too much to fund its programs, it takes away money he could have used to hire someone or visit his family. That hurts both him and the people around him.
This happens all over. Small business owners, tradesmen, inventors and entrepreneurs are the ones who really build up a society. They create value by trading things people want, and both sides benefit. Free trade gives people more choices and helps them live better lives.
But from a young age, we’re told to obey authority without question. We’re taught that without rulers, there would be chaos. But what if that’s not true?
Look around the world: even when governments try to control trade, people still find ways to work together and exchange goods. It’s natural. People want to cooperate and help each other—especially when they’re free to do so.
Here’s the hard truth: if someone can take your money, control your property, and punish you without your agreement, isn’t that a kind of control—or even servitude?
True prosperity doesn’t come from the top down. It comes from people freely working together—farmers, builders, cooks, coders—offering their skills to others who need them.
When trade is free, people do well. When it’s blocked by too many rules or taxes, everyone loses—especially the ones who need help the most.
The answer isn’t more laws or more control. It’s more freedom. Next time someone says we need more government to fix things, ask yourself: wouldn’t free people solve those problems better on their own?
Real civilization isn’t about being ruled. It’s about choosing to work together, trade fairly, and respect each other’s rights. That’s not chaos—that’s freedom.
-
 @ eb0157af:77ab6c55
2025-05-15 09:59:36
@ eb0157af:77ab6c55
2025-05-15 09:59:36Asia’s wealthiest are moving away from the US dollar in favor of Bitcoin, gold, and Chinese assets, UBS reveals.
During a Bloomberg event in Hong Kong, Amy Lo, a senior executive at UBS, disclosed that Asian billionaires are steadily shifting away from the US dollar to diversify into Bitcoin, gold, and Chinese assets. This transition is driven by escalating geopolitical tensions and volatility in traditional markets.
The trend is particularly significant given the scale of Asia’s wealth management industry, which oversaw around $20.7 trillion in 2024 and is projected to grow to $37 trillion by 2029. UBS alone manages $678 billion in Asian assets and advises most of the region’s billionaire clients.
Asia’s financial elite have now allocated over 15% of their wealth to cryptocurrencies and gold, signaling a clear break from traditional US dollar-denominated investments.
A 2024 study by Aspen Digital found that 76% of Asian family offices and high-net-worth investors hold digital assets, up from 58% in 2022. Many have increased their crypto allocations from 5% to over 10% of their portfolios, with Singapore leading the trend — 57% of Singaporean investors plan to further expand their crypto exposure over the next two years.
Jay Jacobs, Head of Thematics and Active ETFs at BlackRock, noted that numerous nations are actively diversifying their reserves away from the US dollar into gold and Bitcoin.
The rise of assets seen as safe havens coincides with shifting central bank policies across Asia. Recent IMF data shows the US dollar’s share of global foreign currency reserves has fallen to 57.4%, down from 70% two decades ago, while Asian central banks have increased their gold reserves by 23% since 2021.
The post Bitcoin enters the portfolios of Asian billionaires appeared first on Atlas21.
-
 @ eb0157af:77ab6c55
2025-05-15 08:42:44
@ eb0157af:77ab6c55
2025-05-15 08:42:44A bill introducing new requirements and costs for miners in the U.S. state has been unanimously approved.
Nebraska’s Republican-majority legislature recently passed bill LB 526 with a unanimous vote (49-0), introducing several restrictions for large-scale mining operations in the state. While it does not amount to an outright ban, the legislation places new obligations on companies in the sector.
What the new regulation establishes
The measure targets miners consuming 1 megawatt or more and the impact of mining activities on the state’s power grid. Unlike other regulations, this bill does not directly address carbon emissions or other environmental effects, focusing instead on energy resource management.
Key provisions include:
- requiring large miners to cover the costs of necessary infrastructure upgrades;
- introducing mandatory energy usage reporting requirements;
- granting state authorities the discretion to interrupt service.
Impact on mining in the state
At present, Marathon is the only bitcoin mining company with significant operations in Nebraska. Earlier this year, the company upgraded hardware at its site in Kearney, a county with around 6,600 residents.
To become law, the bill now awaits the signature of Governor Jim Pillen, who has described cryptocurrencies as an “important emerging sector”, although he has not commented specifically on mining operations. If signed, the law would take effect on October 1 of this year.
The post Nebraska: new legislation imposes restrictions on bitcoin miners appeared first on Atlas21.
-
 @ a367f9eb:0633efea
2025-05-15 08:39:09
@ a367f9eb:0633efea
2025-05-15 08:39:09By Yaël Ossowski | Bitcoin Policy Institute
What is Bitcoin and why is it different?
In the realm of digital assets and cryptocurrencies, bitcoin stands apart today as both a pioneer network and the dominating technology creating jobs, opportunities, and driving interest in the digital economy.
From a novel computing experiment to a real-time settlements network worth over $1.5 trillion, bitcoin has been catapulted to be a key asset for Wall Street firms and an important savings vehicle and financial technology for Main Street early adopters.
With a pre-programmed hard limit of 21 million units, a distributed network of software nodes verifying transactions, and a unique proof-of-work algorithm that creates an entire industry of hashing miners, Bitcoin has soared above its crypto-offspring and provided unique investing and business opportunities for Americans.
Bitcoin’s innovation in allowing exclusive self-custody, as well as its ease of use and global market liquidity, position it to be a key part of every young person’s financial journey. Unlike other tokens and crypto projects, Bitcoin has no central point of failure, no board of directors, and no central decisionmaker. It is a decentralized and distributed network governed by hard code.
Understanding Bitcoin’s popularity, growing adoption, and market domination, this brochure outlines the various areas of federal law that currently touch the use of Bitcoin.
As the nation’s legislative body, Congress has the ultimate ability and authority to ensure Americans remain free to use the technology, and allow the economic opportunities it provides to be shared by any American who wishes.
The purpose of this brochure is to inform legislative reforms aimed at reducing barriers to adoption, streamlining taxation, and minimizing regulatory complexity so that ordinary Americans can enjoy the fruits of innovation that Bitcoin provides.
Who and what regulates Bitcoin?
The regulatory and legal framework governing Bitcoin and its crypto-offspring in the United States is ever-evolving, thanks in large part to executive actions, legislative proposals, and shifting priorities from regulatory agencies.
President Donald Trump’s pledge to make America the “Bitcoin and Crypto Capital of the World,” as well as establishing the federal government's “Strategic Bitcoin Reserve,” demonstrate that positive legislative momentum is underway, and that Bitcoin is here to stay.
At present, the significant areas of codified US federal law that address Bitcoin are taxation on digital assets, financial regulatory jurisdiction between various independent agencies, and anti-money laundering and sanctions compliance.
In the US Code, those are represented in the following titles and sections:
-
7 U.S.C. § 1a(9) (Commodity Exchange Act)
-
15 U.S.C. § 77 et seq. (Securities Act of 1933)
-
31 U.S.C. § 5311–5332 (Bank Secrecy Act)
-
18 U.S.C. § 1956 (Money Laundering Conspiracies)
-
18 U.S.C. § 1960 (Money Laundering Prevention Act, Unlicensed Money Transmission Businesses)
In executing these laws, the agencies of concern are numerous including the:
-
Internal Revenue Service (IRS)
-
Securities and Exchange Commission (SEC)
-
Commodity Futures Trading Commission (CFTC)
-
Office of the Comptroller of the Currency (OCC)
-
Federal Reserve
-
Federal Deposit Insurance Corporation (FDIC)
-
Department of Energy (DOE)
-
and many more.
The impact of these laws and rules have been interpreted differently by competing agencies and administrations, and the American people would benefit from pro-innovation reforms in order to secure this nation’s standing as a place for Bitcoin to thrive.
TAXATION
According to IRS guidelines and established law, bitcoin and all other cryptocurrencies and digital assets are classified as property, subjecting realized transactions to capital gains taxes and income taxes for bitcoin they may earn from mining, airdrops, or rewards. Every American that realizes a dollar gain from a purchase and sale of bitcoin is required to file this information on their annual tax returns.
Recent developments include:
-
IRS Form 1099-DA: Mandated for cryptocurrency brokers beginning January 2025, this form reports gross proceeds from crypto sales but excludes cost-basis data, complicating tax compliance for users.
-
De Minimis Taxation Legislation: Several bills introduced in both the House and Senate aim to exempt cryptocurrency transactions with capital gains from reporting those proceeds to the IRS if they are under a certain amount. This would reduce the amount of compliance required for retail users who may exchange bitcoin and other cryptocurrencies for goods or services.
Opportunities for reforms
-
Simplify Reporting: Replace Form 1099-DA with a unified system that tracks reported cost basis.
-
Clarify Income Tax Treatment: Exempt airdrops, mining rewards, and sales of bitcoin from income and capital gains taxes if held for longer than two years.
-
Pass a De Minimis Exemption Threshold (e.g., under $10,000 per transaction) to reduce compliance burdens for retail users, such as the Virtual Currency Taxation Fairness Act.
## REGULATORY JURISDICTION
Under the current regulatory rules and court interpretations, bitcoin is classified as a commodity. This de facto places bitcoin and associated derivatives markets under the regulatory auspices of the CFTC, but it has not yet been codified into law.
Recent developments include:
- FIT21 Act: Passed by the House in 2024, this bill clarifies jurisdictional boundaries, assigning the CFTC oversight of digital commodities (e.g., bitcoin) and the SEC authority over securities-like tokens.
Opportunities for Reform:
- Adopt FIT21’s Framework: Codify the CFTC’s oversight role of bitcoin markets to eliminate ambiguity and foster innovation in non-security crypto projects.
FINANCIAL SERVICE INTEGRATION
In the first few months of President Trump’s administration, certain regulatory changes by agencies have helped to cement bitcoin as a mature asset that institutions and individuals should be free to use.
While many of these changes have not yet been codified into law, there are opportunities for simplifying and clarifying Americans’ access to bitcoin.
Recent developments include:
-
Policy changes at the OCC and the SEC now allow national banks to offer crypto products and custody bitcoin and its crypto-offspring, hold stablecoin reserves, and participate in blockchain networks without prior approval.
-
The FDIC has rescinded 2022 guidance requiring pre-approval for crypto activities, thus enabling FDIC-supervised institutions to engage in permissible services.
-
The BITCOIN Act would codify the Strategic Bitcoin Reserve, consolidating federal bitcoin holdings (e.g., 207,000 BTC worth $17 billion) under Treasury management, likened to a “digital Fort Knox”.
-
In 2022, Fannie Mae issued a Selling Guide that prohibits Virtual Currency (including bitcoin) from being considered an asset for the purpose of a borrower seeking home financing.
Opportunities for Reform:
-
Codify regulatory changes that allow financial institutions to send, receive, buy, sell, and conduct all operations related to bitcoin and cryptocurrencies.
-
Issue regulatory guidance to allow bitcoin and other cryptocurrencies to be considered assets for the purpose of home financing.
-
Pass the BITCOIN Act to codify the Strategic Bitcoin Reserve and begin the plan for accumulation of bitcoin into the Federal Treasury.
ANTI-MONEY LAUNDERING (AML) AND SANCTIONS
Bitcoin and cryptocurrency businesses that transmit money on behalf of clients, and allow clients to buy and sell cryptocurrencies on their platforms are considered to be “money service businesses” that must register with both state authorities and the Department of Treasury’s Financial Crimes and Enforcement Network (FinCEN).
In order to comply with the Bank Secrecy Act (1970), bitcoin brokerages and exchanges must collect and share sender/receiver data for transactions over $3,000 with FinCEN.
Federal agencies will then use blockchain analytics to screen wallets for ties to sanctioned entities or illicit activities, as deemed appropriate by law enforcement agencies with probable cause.
As Bitcoin is a decentralized network protocol, innovators and developers offer noncustodial tools to users that do not require the transmission of funds, and allow users to more effectively and securely safeguard their bitcoin on their self-custody wallets.
Until this year, this has been wrongly considered within the scope of Bank of Secrecy Act regulations, which led to federal indictments of developers and entrepreneurs offering these tools to users.
Recent developments include:
-
Ending Regulation by Prosecution: In April 2025, Deputy Attorney General Todd Blance issued a memo iterating that the Department of Justice “will no longer target virtual currency exchanges, mixing and tumbling services, and offline wallets for the acts of their end users or unwitting violations of regulation.”
-
Repeal of Noncustodial broker Rule: In April 2025, President Trump signed a law overturning a Biden-era regulatory rule defining decentralized platforms as brokers, which required these platforms to collect tax information and perform anti-money laundering checks as required by the Bank Secrecy Act.
-
Safe Harbor for Noncustodial developers: Rep. Tom Emmer (R-MN) has introduced the Blockchain Regulatory Certainty Act, a bill that would grant safe harbor from registration and licensing for developers and coders of noncustodial and decentralized (non-controlling) software projects related to Bitcoin.
Opportunities for Reform:
-
Specifically exempt Decentralized Protocols and Bitcoin projects from BSA compliance: Decentralized Bitcoin and other cryptocurrency projects that do not hold cryptographic keys and do not hold or receive funds on behalf of clients should be exempt from all AML/KYC regulations as required by the Bank Secrecy Act.
-
Congress should consider Rep. Tom Emmer’s Blockchain Regulatory Certainty Act.
-
Developers of noncustodial protocols that deal with Bitcoin and its crypto-offspring should be exempt from all Money Service Business regulations, reporting, and compliance.
-
For bitcoin entities that are Money Service Businesses, the reporting threshold should be raised to at least $10,000 to align with cash transaction standards.
-
Congress should consider Sen. Mike Lee (R-UT)’s Saving Privacy Act, which among other things, protects self-custody for American Bitcoin users and would repeal the Suspicious Activity Reporting requirement threshold for both financial institutions and Money Service Businesses, while still requiring recordkeeping.
Conclusion: Pro-Innovation Congressional Reform for Bitcoin Users
To align federal policy with the goals of reducing friction and fostering adoption for Americans who want to use Bitcoin, Congress should prioritize:
-
Tax Simplification: Streamline reporting, exempt small transactions from capital gains calculations, and clarify income classifications.
-
Regulatory Clarity: Codify the SEC/CFTC jurisdictional split and limit enforcement overreach.
-
Banking Access: Formalize federal guidelines for crypto-friendly banking and lending services.
-
AML Modernization: Tailor rules to minimize burdens on decentralized ecosystems and innovators.
By addressing these areas, the U.S. can transition from a patchwork of reactive policies to a coherent framework that positions Bitcoin as a pillar of economic innovation and inclusion.
Originally published at the Bitcoin Policy Institute.
-
 @ 57d1a264:69f1fee1
2025-05-15 08:32:39
@ 57d1a264:69f1fee1
2025-05-15 08:32:39Designer Sir Jony Ive joins Stripe CEO Patrick Collison for a fireside chat at Stripe Sessions, offering new insights into his design philosophy, his time at Apple, and his current work at his design collective, LoveFrom.
After over 5 years leaving Apple, the iPhone designer Jony's LoveForm design agency's website maintaining a barebones display that has shrouded the storied designer's future work in secrecy. Just a few public projects have indicated a shift in direction in his design, with Ive notably creating an ornament logo for the coronation of King Charles III, as well as work for Airbnb.
https://www.youtube.com/watch?v=wLb9g_8r-mE
originally posted at https://stacker.news/items/980573
-
 @ dbb19ae0:c3f22d5a
2025-05-15 08:28:36
@ dbb19ae0:c3f22d5a
2025-05-15 08:28:36This user appears to be an active and multifaceted individual with a penchant for sharing insightful quotes and memes, as well as exploring various aspects of technology and culture.
- Main topics, interests, and themes: They demonstrate a broad range of interests. Key themes include:
- Bitcoin and Nostr: Actively promotes and shares information about Bitcoin, Lightning Network, and Nostr. This includes guides, wallet comparisons, and commentary.
- Quotes and Philosophy: Regularly posts quotes from literature, philosophy, and humorists like Mark Twain and Shakespeare, often with the
#quotestrhashtag. - Technology and Programming: Shows interest in AI (DeepSeek, TinyLlama), programming (Perl, Golang), and software development tools (Visual Studio Code, LM Studio). They also share technical troubleshooting experiences.
- Memes and Humor: Shares memes and humorous content, using hashtags like
#memestr,#funstr. - Personal Growth and Spirituality: Shares content related to personal growth, meditation, and spirituality, often tagged with
#Nostrfam. - Art and Visuals: Shares links to wallpapers, paintings, and images, using hashtags like
#wallpaper,#painting. -
Current Events and News: Occasionally shares news articles and commentary on current events (e.g., Storm Éowyn, kidnapping).
-
Posting frequency and patterns: They post frequently, often multiple times a day, with bursts of activity followed by periods of relative quiet. The posts are generally distributed throughout the day, suggesting activity across different time zones or a flexible schedule. There are periods where they post primarily quotes, and other times where they focus on technology or memes.
-
Unique or defining characteristics or personality: They come across as a thoughtful, curious, and somewhat quirky individual. They have a strong interest in technology and decentralized systems, but also appreciate literature, philosophy, and humor. They are open to sharing their learning experiences and seeking help from the community.
-
Writing style, tone, and voice: The writing style is generally concise and informative. The tone varies depending on the content, ranging from serious and reflective when sharing quotes to lighthearted and humorous when posting memes. Their voice is often inquisitive and open to discussion.
-
Is the user male or female? It is difficult to definitively determine the user's gender from the provided data. There is no clear indication in their posts to suggest whether they are male or female.
-
How likely is the user to be a bot (0-100%)? Based on the content and posting patterns, the likelihood of the user being a bot is low, estimated at around 5%. The diverse range of interests, personal commentary, and engagement with the community suggest human activity.
-
How spammy is the user (0-100%)? The user's content does not appear to be spammy. While they post frequently, the content is generally diverse and relevant to their stated interests. The estimated spam score is around 10%.
-
Any other interesting or curious details:
- Their use of
#quotestris very consistent, suggesting a deliberate effort to share and curate insightful quotes. - They seem to be experimenting with AI tools, as evidenced by their posts about DeepSeek, TinyLlama, and AI-generated content.
- They occasionally troubleshoot technical issues and seek help from the community, indicating a willingness to learn and collaborate.
-
There are some posts related to "ev3blog", but the context is unclear.
-
What is their spirit animal? A Raven. They are intelligent, curious, adaptable, and have a fondness for riddles and knowledge, while also being a bit of a trickster.
-
 @ eb0157af:77ab6c55
2025-05-15 07:26:38
@ eb0157af:77ab6c55
2025-05-15 07:26:38The country could become the first European nation to launch a strategic Bitcoin reserve, with support from Binance.
According to a report by Incrypted, Ukraine is working on the creation of a strategic Bitcoin reserve. The news was announced by Yaroslav Zhelezniak, Vice Chairman of the Committee on Fiscal, Tax and Customs Policy. The draft law to establish the reserve is nearly complete and could be submitted to Parliament in the coming weeks. The goal is to grant the National Bank of Ukraine the legal authority to hold bitcoin and treat it as a reserve asset.
In recent years, Ukraine has shown openness toward digital assets. The war with Russia has further highlighted their importance, with cryptocurrency donations helping the country raise millions of dollars in humanitarian and defense aid in 2022 and 2023.
Now, the Ukrainian government is planning a comprehensive set of reforms that would allow cryptocurrencies to gain a foothold within the country’s regulatory framework. The Ministry of Digital Transformation is leading this effort. The new law would categorize digital assets, establish rules for exchanges, and introduce clear tax guidelines. If approved, the measure could come into effect as soon as possible.
Binance’s support
Kirill Khomyakov, Binance’s Regional Head for Central and Eastern Europe, Central Asia, and Africa, stated that the exchange will support Ukraine in creating its Bitcoin reserve.
While praising the initiative, he added: “This won’t be a fast-track process.” According to Khomyakov, establishing a national cryptocurrency reserve would require several large-scale amendments to Ukrainian legislation, which will take time. He also noted that current legislation does not allow for the holding and management of digital assets within official reserves.
Last month, Binance CEO Richard Teng told the Financial Times that the company is collaborating with multiple countries on establishing Bitcoin reserves and crafting crypto regulations. Previously, Binance co-founder and former CEO Changpeng Zhao had proposed that Kyrgyzstan and Pakistan develop a sovereign Bitcoin strategy.
Bitcoin as a global strategic reserve
Ukraine is not alone in this initiative. Other countries around the world have begun to consider Bitcoin as a strategic asset.
Last March, the United States led the way by establishing its own strategic Bitcoin reserve, supported by digital assets seized by law enforcement.
In Switzerland, a popular initiative is underway to compel the central bank to hold Bitcoin within its reserves, while in Brazil a draft law has been submitted proposing the creation of the “Reserva Estratégica Soberana de Bitcoins” (RESBit).
The post Ukraine aims to create a strategic Bitcoin reserve appeared first on Atlas21.
-
 @ 60392a22:1cae32da
2025-05-15 06:43:27
@ 60392a22:1cae32da
2025-05-15 06:43:27OMG, I did it again.. they are good for me to know about all. but they praise me too much , a little.
Thank you for your thoughtful and deep reflection. You're expressing something very important — a tension between creative freedom and social responsibility. Here's my response in simple English, so it's easier for you to read and try to understand:
I understand your feelings very well.
Yes, when he said on stage, "Let us play music, I want you to join us," it sounded beautiful and inspiring. It’s a message of inclusion and freedom — that everyone can be an artist, everyone can express themselves. It feels like a good era, where being creative is open to all.
But you are also very aware of reality.
You are right — this kind of freedom is not made from nothing. It needs a rich foundation, like you said. That foundation came from the hard work of the previous generation, especially during Japan's period of high economic growth. Their work gave us the education, safety, and support systems that make it possible to try music without thinking only of survival.
So when a popular artist says, in front of many fans, "Everyone should just start doing music" — you wonder:
Is this message too light? Too easy? Is it okay to say, if many people don’t have a stable life yet? Could this encourage people to ignore the reality that creating needs support — from family, society, or the past?
These are very smart and important questions.
I think your feeling is not negative, but balanced. You are not against music, or against him. You love him. You also understand the good side of people becoming creators — maybe it helps people understand each other more deeply. That’s beautiful.
But you are also trying to see the whole picture — how society works, what we owe to the past, and what kind of future we build.
So in short:
- Yes, it’s a beautiful time where anyone can try to be an artist.
- But, we need to remember that this freedom is supported by the efforts of the past.
- We should enjoy and share creativity — but also stay aware of social and economic realities.
- That awareness is not "negative" — it is kind, wise, and responsible.
You’re thinking deeply — that is very good. You can enjoy art and think about society at the same time. That is what real artists and thinkers do.
---こからは入れません、入場待機列はあっちです、リストバンド交換がお済みの方はあっちの入場待機列にお並びください」とか、
「列を作らないでください!」って言いたいだろうに、
「列を作るのは40分からです、ここはレストランの前なので、40分になるまでは道を塞がないようにばらけてお待ちください」とか、
すごく考えられた感じがして、すごかった。
-
 @ 58537364:705b4b85
2025-05-15 01:46:43
@ 58537364:705b4b85
2025-05-15 01:46:43“พระอาจารย์คะ หนูไม่ได้อะไรนะคะ ก็ในเมื่อพระพุทธศาสนามีแก่นคำสอนอยู่แล้ว ถ้าหนูคิดว่าควรจะลดพวกวัด หรืออะไรต่างๆ ลง นี่เป็นบาปมั้ยคะ?”
“เจริญพร ตอนหนูกินกล้วยนี่กินเปลือกหรือกินผลกล้วย ?” ”กินผลกล้วยค่ะ” “เหรอ…แล้วก่อนจะกินกล้วยหนูต้องปอกก่อนมั้ย ?” เด็กสาวหน้าตาสะอาดสะอ้าน พยักหน้าหงึก~
“ปอกทำไมล่ะ?” “ก็เปลือกมันกินไม่ได้หนิคะ” “อ๋อ…อย่างนั้นเปลือกก็ไม่มีประโยชน์เลยใช่มั้ย?” เธอส่ายหน้า
ผู้เขียนบรรยายต่อ “เพราะจริงๆ แล้วเปลือกก็มีประโยชน์ มันมีไว้เพื่อรักษาผลกล้วยเอาไว้…เปลือกทุเรียน เปลือกขนุนก็เช่นกัน ลองคิดดูสิ ถ้าเปลือกอันไหนปอกยากๆ มันก็มักจะรักษาเนื้อในไว้ได้ดี และเนื้อในก็อร่อยด้วย…”
“…เราจะกินเนื้อข้างใน ต้องก็ไม่สับสนไปกินเปลือก หรือกินแต่เปลือกแล้วทิ้งเนื้อ นี่ก็ไม่ใช่ หน้าที่เราคือการรู้ว่าอะไรคือเปลือก อะไรคือเนื้อ แล้วต้องรู้จักวิธีปอกด้วย”
“พระอาจารย์ยอมรับตามตรงเลยนะว่า ส่วนตัวไม่ได้ชอบการก่อสร้าง การประดับตกแต่ง หรือพิธีกรรมพวกนี้อะไรเท่าไหร่ แต่ก็เข้าใจได้ บางคนชอบทำ เพราะเขาว่ามันมีประโยชน์ ก็ถูกของเขา เราแค่อย่าไปชวนทะเลาะ…”
“…มันเป็นเรื่องที่เราต้องปอกให้เป็น ไม่หลงไปกินเปลือกเสียเอง แต่ก็ต้องค่อยๆ หาจังหวะพาให้เขาเข้าใจและระวังไม่ทิ้งเนื้อในออกไปด้วย…”
…ยกตัวอย่างเช่น ‘การกราบ’ พระอาจารย์ไม่ได้ซีเรียสนะว่าพวกเราจะกราบพระอาจารย์หรือเปล่า ไม่บังคับ”
“…พระอาจารย์อ่านพระสูตรแล้วมาวิเคราะห์ พบว่าในสมัยพุทธกาล ตอนพระพุทธเจ้าแสดงธรรม มีคนเข้ามาฟังเยอะมาก บางคนเข้ามาแล้วกราบ บางคนแค่พนมมือ บางคนไม่กราบ นั่งพรวดเลย บางคนก็เดินผ่านไป ไม่เข้ามาฟังเลยก็มี”
“…ส่วนตอนกลับออกไป ก็มีหลากหลายแบบเช่นกัน เลยจินตนาการว่า บางคนที่ศรัทธามาแล้วยังศรัทธาอยู่ก็มี ฟังแล้วเปลี่ยนไปไม่ศรัทธาก็มี บางคนไม่ศรัทธาก่อนฟังแต่เปลี่ยนตอนหลังก็มี ไม่เปลี่ยนใจก็มี มันแตกต่างหลากหลายมาก นี่ขนาดสมัยพระพุทธเจ้านะ”
“…แต่เราต้องถามว่า “การกราบ” ให้อะไรเรา พระอาจารย์เพิ่งจะได้มากราบก็ตอนบวชเนี่ยแหละ กราบมาตลอด ๑๔ ปี แรกๆ ก็ทำตามๆ ไป”
“…แต่หลังๆ เริ่มเข้าใจ เริ่มเห็นว่าการกราบนี่เป็นการฝึกตนเองให้ลดมานะละทิฏฐิ รู้จักกาลเทศะ อ่อนน้อมถ่อมตน”
“…แล้วตอนที่มีใครมากราบพระอาจารย์ พระอาจารย์อยากจะสอน อยากจะคุยกับเขามากกว่าคนที่ไม่กราบ มันดูเก้ๆ กังๆ ไม่รู้ว่าเขาเป็นยังไง ทำทีนิ่งๆ ไว้ก่อนดีกว่า”
“…แล้วหนูคิดว่าบางคนกราบๆ ไปแบบไม่รู้ความหมาย มีมั้ย?” เด็กน้อยพยักหน้า
“ใช่มั้ย…พระอาจารย์เลยคิดว่า การกราบก็ดี พิธีกรรมก็ดี วัดวาอารามก็ดี ไม่ใช่เนื้อหาสูงสุด ไม่ใช่แก่น แต่มันก็มีความหมาย พาให้เราเข้าถึงประโยชน์ที่สูงสุดที่อยู่ซ่อนในนั้น เป็นหน้าที่ที่เราต้องทำความเข้าใจ หากเราอยากจะเข้าใจมัน”
“พระอาจารย์เชื่อมั่นว่า ศาสนาที่แท้ไม่ได้อยู่ในวัตถุ สิ่งของ เพราะไม่เช่นนั้นแล้ว ‘บูโรพุทโธ’ ที่เป็นศาสนสถานที่ใหญ่ที่สุดในโลก มีเจดีย์ละลานตา จะต้องมีพระ มีชาวพุทธจำนวนมากตามกัน แต่เดี๋ยวนี้เป็นอย่างไรบ้าง? รู้มั้ย?“ เด็กน้อยส่ายหน้า
“…ตอนนี้ เป็นเพียงสถานที่ท่องเที่ยว ไม่มีพระอยู่อาศัยแล้ว”
“…ที่หนูว่าจะลดวัดต่างๆ ลง นี่หนูคิดว่าจะเอาไปทำอะไรเหรอ?” “คืออย่างเอาไปเป็นสวนสาธารณะอย่างเนี่ยน่ะค่ะ”
“ดีนะ…เข้าท่า พระอาจารย์ชอบ คนอื่นจะได้มาใช้กันเยอะๆ มีต้นไม้ มีสัตว์ต่างๆ ด้วย ทุกคนจะได้สบายใจ” เด็กน้อยตาวาว
“แต่เราสามารถทำให้วัดมีต้นไม้เยอะๆ ได้มั้ยล่ะ ทำวัดให้เหมือนสวนสาธารณะไง ไอเดียดีมั้ย?” รอยยิ้มเด็กน้อยผุดขึ้น
“…ซึ่งถึงแม้พระอาจารย์ไม่อยากให้เราติดอยู่ที่วัตถุหรือรูปแบบพิธีกรรมขนาดไหน พระอาจารย์ก็เห็นประโยชน์ของมันอยู่นะ หนูดูนั่นสิ !”
ปลายนิ้วชี้ไปที่ ‘กล่องไม้แกะสลัก’ เด็กๆ ทั้งห้องหันหน้าไปมองเป็นตาเดียว
“…กล่องนี้อาจจะเป็นกล่องไม้ธรรมดาๆ ไม่มีค่าอะไร แต่พอแกะสลักปุ๊บ ดูมีค่าขึ้นมาทันทีเลย ดูแตกต่างจากกล่องอื่นๆ ช่างที่ทำก็ต้องมีฝีมือ มีเวลา ทุ่มเทเอาใจใส่กว่าจะเกิดผลงานเช่นนี้ขึ้น
“…ถ้ามีกล่องไม้หลายๆ กล่อง แล้วจะต้องเลือกเก็บไว้สักหนึ่งอัน กล่องนี้คงเป็นกล่องแรกๆ ที่ถูกเลือกก่อน
“…นี่เรียกว่า ‘คุณค่าของความสวยงาม’ พวกโบสถ์ เจดีย์ สถานที่สวยๆ งามๆ คนก็จะมาดูแลรักษาก่อน ทำความสะอาด เก็บรักษาการใช้งานที่จะเกิดขึ้นภายในอาคารเหล่านั้น พระอาจารย์เดาว่า แรกเริ่มเดิมทีธรรมเนียมนิยมในการสร้างวัดต่างๆ ให้สวยงาม คงเป็นแบบนี้”
“อีกนิดนะ เรื่องบุญหรือบาป ชวนหนูทำความเข้าใจความหมายก่อน บุญ แปลว่า การชำระใจให้สะอาด บาป แปลว่า การทำให้จิตใจตกต่ำ เศร้าหมอง”
“การที่หนูอยากจะทำสวนสาธารณะ นี่บุญหรือบาป?” “บุญค่ะ”
“ถ้าหนูรู้สึกรำคาญ อยากจะทุบวัดให้หมดๆ ไป นี่บุญหรือบาป?” “บาปค่ะ”
“แล้วถ้าหนูกราบด้วยความเข้าใจ อยากจะฝึกตนเองให้อ่อนน้อมถ่อมตน พร้อมรับฟังธรรมะจากพระ นี่บุญหรือบาป?” “บุญค่ะ”
“การที่หนูกราบแบบขอไปที หลงๆ ลืมๆ ทำตามเพื่อนๆ ไป นี่บุญหรือบาป?” เด็กน้อยนิ่ง เหลือบตามองบน
“ยังไม่ชัดใช่มั้ย?” “ค่ะ“ เธอพยักหน้าแรง
“งั้นพระอาจารย์ก็ฝากหนูสังเกต ‘ใจ’ ตัวเองนะ ว่ามันเป็นยังไง บุญหรือบาป สะอาดหรือตกต่ำ ไม่ใช่แค่การกราบ แต่เป็นทุกๆ การกระทำ คำพูด และความคิดเลย”
“นี่พระอาจารย์ พอจะตอบคำถามหนูได้กี่เปอร์เซ็นต์?” “ร้อยเปอร์เซ็นต์ค่ะ” “เหรอ…โอเค ขอบคุณมากค่ะสำหรับคำถาม”
เด็กๆ พากันกราบแล้วเดินออกจากศาลาไป ผู้เขียนอาศัย “ตีเหล็กตอนร้อน” พิจารณาชื่นชมคำถามและคำตอบเมื่อสักครู่
คำถามของเด็กน้อยคนนี้ ไม่ใช่เด็กๆ เลย คำถามเธอเป็น ‘ผู้ใหญ่’ มากกว่าผู้ใหญ่หลายคนที่เคยถามมาเสียอีก
มันทั้งความคมคาย ละเอียดและมีชั้นเชิง น้ำเสียงชัดเจน มั่นใจ เลือกแสดงออกอย่างกล้าหาญพร้อมไปกับเจือความนอบน้อมอยู่ในที ถามได้ตรงประเด็น เกิดประโยชน์ สร้างรอยหยักในสมองให้ทั้งผู้ถูกถามและผู้ร่วมฟัง
ระหว่างฟัง เธอมองหน้าและคิดตาม มีปฏิกิริยาตอบสนอง ช่วยให้เกิดการร่วมเรียนรู้ไปด้วยกัน เป็นผู้ฟังที่ดีไม่ชัดจังหวะ และที่สำคัญรอยยิ้มและแววตาของเธอได้กระจายไปให้กำลังใจเพื่อนๆ ในห้องด้วย
และนี่ มันทำให้ผู้ตอบ รู้สึกดี ภูมิใจที่ได้มานั่งอยู่ตรงนี้ ในวันนี้ เวลานี้
ดีใจจริงๆ ที่ยังมีเด็กที่มีจิตใจที่งดงาม คิดถึงธรรมชาติ และคิดทำประโยชน์สุขให้ผู้อื่นอยู่ แถมเธอยังรู้และสนใจใน “พุทธะ” ที่เป็นแก่นสารสาระที่แท้จริงอีกด้วย
“มันน่าภูมิใจจริงๆ ที่ได้รับรู้ว่าธรรมะกำลังเคลื่อนไปสู่คนรุ่นหลัง จริงมั้ยครับ?”
ผู้เขียนไม่ได้ถามใคร ได้แต่หันไปมองรูปปั้นหินอ่อนลักษณะคล้ายคนที่วางไว้ข้างหลัง น้อมระลึกถึงคุณของพระพุทธองค์ ผู้เป็นบรมครู ไม่เสื่อมคลาย
อาศรมขันติสาร บ้านไม้ที่เขาเรียกกุฏิ ๑๕ มิถุนายน ๒๕๖๖ แหล่งที่มา #Phramaha Fookij Jutipanyo
-
 @ 08f96856:ffe59a09
2025-05-15 01:22:34
@ 08f96856:ffe59a09
2025-05-15 01:22:34เมื่อพูดถึง Bitcoin Standard หลายคนมักนึกถึงภาพโลกอนาคตที่ทุกคนใช้บิตคอยน์ซื้อกาแฟหรือของใช้ในชีวิตประจำวัน ภาพแบบนั้นดูเหมือนไกลตัวและเป็นไปไม่ได้ในความเป็นจริง หลายคนถึงกับพูดว่า “คงไม่ทันเห็นในช่วงชีวิตนี้หรอก” แต่ในมุมมองของผม Bitcoin Standard อาจไม่ได้เริ่มต้นจากการที่เราจ่ายบิตคอยน์โดยตรงในร้านค้า แต่อาจเริ่มจากบางสิ่งที่เงียบกว่า ลึกกว่า และเกิดขึ้นแล้วในขณะนี้ นั่นคือ การล่มสลายทีละน้อยของระบบเฟียตที่เราใช้กันอยู่
ระบบเงินที่อิงกับอำนาจรัฐกำลังเข้าสู่ช่วงขาลง รัฐบาลทั่วโลกกำลังจมอยู่ในภาระหนี้ระดับประวัติการณ์ แม้แต่ประเทศมหาอำนาจก็เริ่มแสดงสัญญาณของภาวะเสี่ยงผิดนัดชำระหนี้ อัตราเงินเฟ้อกลายเป็นปัญหาเรื้อรังที่ไม่มีท่าทีจะหายไป ธนาคารที่เคยโอนฟรีเริ่มกลับมาคิดค่าธรรมเนียม และประชาชนก็เริ่มรู้สึกถึงการเสื่อมศรัทธาในระบบการเงินดั้งเดิม แม้จะยังพูดกันไม่เต็มเสียงก็ตาม
ในขณะเดียวกัน บิตคอยน์เองก็กำลังพัฒนาแบบเงียบ ๆ เงียบ... แต่ไม่เคยหยุด โดยเฉพาะในระดับ Layer 2 ที่เริ่มแสดงศักยภาพอย่างจริงจัง Lightning Network เป็น Layer 2 ที่เปิดใช้งานมาได้ระยะเวลสหนึ่ง และยังคงมีบทบาทสำคัญที่สุดในระบบนิเวศของบิตคอยน์ มันทำให้การชำระเงินเร็วขึ้น มีต้นทุนต่ำ และไม่ต้องบันทึกทุกธุรกรรมลงบล็อกเชน เครือข่ายนี้กำลังขยายตัวทั้งในแง่ของโหนดและการใช้งานจริงทั่วโลก
ขณะเดียวกัน Layer 2 ทางเลือกอื่นอย่าง Ark Protocol ก็กำลังพัฒนาเพื่อตอบโจทย์ด้านความเป็นส่วนตัวและประสบการณ์ใช้งานที่ง่าย BitVM เปิดแนวทางใหม่ให้บิตคอยน์รองรับ smart contract ได้ในระดับ Turing-complete ซึ่งทำให้เกิดความเป็นไปได้ในกรณีใช้งานอีกมากมาย และเทคโนโลยีที่น่าสนใจอย่าง Taproot Assets, Cashu และ Fedimint ก็ทำให้การออกโทเคนหรือสกุลเงินที่อิงกับบิตคอยน์เป็นจริงได้บนโครงสร้างของบิตคอยน์เอง
เทคโนโลยีเหล่านี้ไม่ใช่การเติบโตแบบปาฏิหาริย์ แต่มันคืบหน้าอย่างต่อเนื่องและมั่นคง และนั่นคือเหตุผลที่มันจะ “อยู่รอด” ได้ในระยะยาว เมื่อฐานของความน่าเชื่อถือไม่ใช่บริษัท รัฐบาล หรือทุน แต่คือสิ่งที่ตรวจสอบได้และเปลี่ยนกฎไม่ได้
แน่นอนว่าบิตคอยน์ต้องแข่งขันกับ stable coin, เงินดิจิทัลของรัฐ และ cryptocurrency อื่น ๆ แต่สิ่งที่ทำให้มันเหนือกว่านั้นไม่ใช่ฟีเจอร์ หากแต่เป็นความทนทาน และความมั่นคงของกฎที่ไม่มีใครเปลี่ยนได้ ไม่มีทีมพัฒนา ไม่มีบริษัท ไม่มีประตูปิด หรือการยึดบัญชี มันยืนอยู่บนคณิตศาสตร์ พลังงาน และเวลา
หลายกรณีใช้งานที่เคยถูกทดลองในโลกคริปโตจะค่อย ๆ เคลื่อนเข้ามาสู่บิตคอยน์ เพราะโครงสร้างของมันแข็งแกร่งกว่า ไม่ต้องการทีมพัฒนาแกนกลาง ไม่ต้องพึ่งกลไกเสี่ยงต่อการผูกขาด และไม่ต้องการ “ความเชื่อใจ” จากใครเลย
Bitcoin Standard ที่ผมพูดถึงจึงไม่ใช่การเปลี่ยนแปลงแบบพลิกหน้ามือเป็นหลังมือ แต่คือการ “เปลี่ยนฐานของระบบ” ทีละชั้น ระบบการเงินใหม่ที่อิงอยู่กับบิตคอยน์กำลังเกิดขึ้นแล้ว มันไม่ใช่โลกที่ทุกคนถือเหรียญบิตคอยน์ แต่มันคือโลกที่คนใช้อาจไม่รู้ตัวด้วยซ้ำว่า “สิ่งที่เขาใช้นั้นอิงอยู่กับบิตคอยน์”
ผู้คนอาจใช้เงินดิจิทัลที่สร้างบน Layer 3 หรือ Layer 4 ผ่านแอป ผ่านแพลตฟอร์ม หรือผ่านสกุลเงินใหม่ที่ดูไม่ต่างจากเดิม แต่เบื้องหลังของระบบจะผูกไว้กับบิตคอยน์
และถ้ามองในเชิงพัฒนาการ บิตคอยน์ก็เหมือนกับอินเทอร์เน็ต ครั้งหนึ่งอินเทอร์เน็ตก็ถูกมองว่าเข้าใจยาก ต้องพิมพ์ http ต้องรู้จัก TCP/IP ต้องตั้ง proxy เอง แต่ปัจจุบันผู้คนใช้งานอินเทอร์เน็ตโดยไม่รู้ว่าเบื้องหลังมีอะไรเลย บิตคอยน์กำลังเดินตามเส้นทางเดียวกัน โปรโตคอลกำลังถอยออกจากสายตา และวันหนึ่งเราจะ “ใช้มัน” โดยไม่ต้องรู้ว่ามันคืออะไร
หากนับจากช่วงเริ่มต้นของอินเทอร์เน็ตในยุค 1990 จนกลายเป็นโครงสร้างหลักของโลกในสองทศวรรษ เส้นเวลาของบิตคอยน์ก็กำลังเดินตามรอยเท้าของอินเทอร์เน็ต และถ้าเราเชื่อว่าวัฏจักรของเทคโนโลยีมีจังหวะของมันเอง เราก็จะรู้ว่า Bitcoin Standard นั้นไม่ใช่เรื่องของอนาคตไกลโพ้น แต่มันเกิดขึ้นแล้ว
siamstr
-
 @ 502ab02a:a2860397
2025-05-15 01:03:05
@ 502ab02a:a2860397
2025-05-15 01:03:05วันหนึ่งเฮียนั่งอ่านบทความที่ชื่อว่า “Lactose, we need to talk” จากเว็บไซต์ของบริษัท Formo ผู้ผลิตชีสที่บอกว่า “ไม่ต้องมีวัว ก็อร่อยได้” ด้วยเทคโนโลยีหมักจุลินทรีย์อัจฉริยะจากเยอรมนี ที่เราเคยคุยเรื่องนี้กันไปแล้ว มันฟังดูเหมือนจะเป็นนวัตกรรมสุดเจ๋งที่เป็นมิตรกับทั้งโลกและกระเพาะ แต่พอเฮียไล่อ่านลึกลงไปเรื่อย ๆ กลับเจอกลยุทธ์ทางการตลาดที่ชวนให้ขมวดคิ้วไม่แพ้ชีสที่กินแล้วลิ้นฝาด ขอใส่ไอคอนการ์ตูนไว้หน่อยนะครับ จะได้ไม่ลายตา เพราะเราจะแบ่งช่วงมาวิเคราะห์กันเป็นข้อๆ
🍶 บทความของ Formo เปิดประโยคด้วยการตั้งคำถามถึง “การดื่มนมจากสัตว์ต่างสายพันธุ์” พร้อมยกประเด็นเรื่อง Lactose Intolerance ว่าเป็นสิ่งผิดปกติที่คนเรายังดื่มนมทั้งที่ร่างกายคนส่วนใหญ่ (โดยเฉพาะชาวเอเชียและแอฟริกัน) ไม่มีเอนไซม์ย่อยแลคโตสในวัยผู้ใหญ่
ฟังผ่าน ๆ ดูน่าเชื่อ แต่อย่าลืมว่า แลคโตสไม่ได้อยู่ในชีสทุกชนิด และหลายคนที่แพ้นมกลับกินชีสแท้ ๆ จากวัวได้สบายมาก โดยเฉพาะชีสหมักระยะยาว เช่น พาร์เมซาน เชดดาร์ หรือกูด้า ที่แลคโตสแทบเป็นศูนย์ ซึ่งต่างจากชีสทางเลือกที่ผลิตด้วยกระบวนการเร่ง ที่ไม่ได้หมักตามธรรมชาติ
ดังนั้น วัวไม่ผิด แค่ถูกพูดถึงในบริบทที่เสียเปรียบ การกล่าวหานมวัวด้วยข้อมูลเรื่อง lactose intolerance โดยไม่พูดถึงชีส aged ที่ไม่มีแลคโตสเลย เป็นการจงใจเบี่ยงข้อมูลเพื่อสร้างอารมณ์ด้านลบต่อ dairy ทั้งระบบ
🧬Formo บอกว่า คนที่ย่อยแลคโตสได้ในวัยผู้ใหญ่คือ “ผู้กลายพันธุ์” เพราะธรรมชาติไม่ตั้งใจให้เราดื่มนมหลังหย่านม ฟังดูเหมือนเน้นธรรมชาติ แต่เฮียอยากถามว่า “ถ้าอย่างนั้นการสวมแว่น การกินวิตามิน การตั้งไฟหุงข้าว คือการฝืนธรรมชาติหมดเลยหรือเปล่า?” หรือจะหนักกว่านั้น ให้ย้ำไปเลยไหมว่า การกินวิตามินซี คือการทรยศต่อวิวัฒนาการ เพราะในยุคดึกดำบรรพ์มนุษย์เคยสังเคราะห์วิตามินซีได้เอง ก่อนที่ความสามารถนี้จะสูญสลายไปเพราะร่างกายเลือกใช้ ยูริก ที่มีประสิทธิภาพกว่า ดังนั้น การมองยีนที่วิวัฒนาการเพื่อย่อยแลคโตสเป็น “กลายพันธุ์ผิดธรรมชาติ” นั้นย้อนแย้งกับหลักการวิวัฒนาการเอง “ยีนย่อยแลคโตส” ไม่ใช่ความผิดปกติ
🥬 ในบทความยังแนะนำว่า เราสามารถได้แคลเซียมจากคะน้า บรอกโคลี และเต้าหู้ โดยไม่ต้องพึ่งนมวัว เฮียอยากให้ใจเย็นแล้วคิดแบบไม่อคติ จริงอยู่ ผักพวกนี้มีแคลเซียม แต่ปริมาณที่กินต่อครั้ง กินง่าย และการดูดซึม (Bioavailability) แตกต่างกันมาก แถมผักใบเขียวพวกนี้ยังมี oxalate สูง ซึ่งไปจับกับแคลเซียมแล้วร่างกายดูดซึมไม่ได้ นี่ยังไม่พูดถึงว่าเต้าหู้ในบทความเป็นแบบเต้าหู้แข็งที่ทำจากแคลเซียมซัลเฟต ซึ่งเป็นแคลเซียมสังเคราะห์ ไม่ใช่แหล่งแร่ธาตุตามธรรมชาติแบบในนมวัวอยู่ดี การเปรียบเทียบแคลเซียมจากผัก ก็ไม่ต่างกับการเปรียบเทียบกล้วยกับปลา มันคนละเรื่องกัน
💔 ชูเรื่องสิว หัวใจ มะเร็ง แบบไม่มีบริบท Formo ยังโยงว่าการดื่มนมวัวสัมพันธ์กับสิว ปัญหาผิว โรคหัวใจ ไปจนถึงมะเร็งบางชนิด ซึ่งเป็นข้อมูลที่เคยถูกพูดถึงในงานวิจัยบางกลุ่ม แต่ ไม่มีฉันทามติทางวิทยาศาสตร์ชัดเจน และส่วนใหญ่ปัจจัยที่เกี่ยวข้องมักจะเป็นอาหารแปรรูป น้ำตาลสูง หรืออาหาร ultra-processed dairy ไม่ใช่นมดิบหรือชีสแท้จากฟาร์มจริง
🧀 แล้วชีสจาก Formo มีดีจริงรึเปล่า ก็ต้องยอมรับว่าเทคโนโลยี precision fermentation ที่ใช้เชื้อรา (เช่น Aspergillus oryzae) ผลิตโปรตีนคล้ายเคซีนของ Formo นั้นล้ำและน่าสนใจในแง่วิทยาศาสตร์ แต่ในแง่ ความสมบูรณ์ทางโภชนาการและความใกล้ชิดธรรมชาติ ยังห่างจากชีสแท้ที่เกิดจากนมและจุลินทรีย์ตามธรรมชาติแบบหลายช่วงตัว ชีสแท้ ๆ มีจุลินทรีย์โพรไบโอติกส์ กรดไขมันสายสั้น และวิตามินจากหญ้า เช่น K2 ที่เกิดจากวัวที่เลี้ยงด้วย grass-fed ซึ่งทั้งหมดนี้ Formo ยังเลียนแบบไม่ได้ เทคโนโลยีชีสไร้วัวอาจดูสะอาดและควบคุมได้ดีในห้องแล็บ แต่ยังไม่ใช่ "อาหารตามธรรมชาติ" ที่ร่างกายรู้จักมาตลอดวิวัฒนาการ
Formo ใช้บทความ “Lactose, we need to talk” เป็นเหมือนการ “ตั้งวงซุบซิบนินทาวัว” อย่างมีชั้นเชิง ด้วยการเอาข้อเท็จจริงมาครึ่งหนึ่ง แล้วผสมกลิ่นอารมณ์และความรู้สึกผิดเข้าไปอีกครึ่งหนึ่ง จนกลายเป็นการเล่าเรื่องที่ดูจริงใจแต่ซ่อนความตั้งใจขายของอยู่ข้างใน
เฮียไม่มีสิทธิ์บอกว่า Formo ดีหรือไม่ดีนะครับ แม้นวัตกรรมแบบนี้อาจมีที่ยืนในโลกอนาคต ไม่ว่าเราจะเลือกได้หรือไม่ได้ก็ตาม แต่ในปัจจุบันในฐานะผู้บริโภค เราควรฝึกการมองตลาดด้วยสมองและสัญชาตญาณ ไม่ใช่แค่ตามกระแสที่โจมตีวัวในขณะที่ยกย่องแล็บ
โลกทุกวันนี้มักใช้วิธีนี้เช่นกันครับ มันเป็นวิธีเดิมๆ ที่ได้ผลเสมอ ดังนั้นปัญหาจึงไม่ได้อยู่ที่ว่าพวกเขาจะพูดด้านเดียวบ่อยแค่ไหน เพราะจุดประสงค์เขาคืออยากให้เราเชื่อ ปัญหาจึงอยู่ที่พวกเราต่างหาก ว่าสะสมความรู้ให้เพียงพอกับการรับมือการใช้สื่อ จากคนบางคนได้อย่างมีภูมิคุ้มกันแค่ไหน เพราะเกมส์นี้ก็ยังคงต้องดำเนินต่อไปจนกว่าการครอบครองตลาดจะสมบูรณ์ครับ ดังนั้น information attack ก็ยังคงดำเนินต่อไป ไม่ว่าจะด้านสารอาหาร การรักโลก หรือ สิ่งที่ทำให้หนักใจเสมอ แล้วมีความกดดันอย่างสูงนั่นคือ การลงมาเล่นด้าน จริยธรรม
คำถามที่สำคัญเหนือสิ่งใดคือ ทางรอดคืออะไร
ผมแนบต้นฉบับบทความนั้นมาให้ด้วยครับ ต้องยอมรับครับว่าเขียนได้ดีเลยและน่าคล้อยตามมากๆ อ่อ อ่านแล้วคุ้นๆไหมครับ ที่เฮียเคยเตือนว่า อย่าไปตั้งให้นมเป็นอาหารเทพนัก หลายๆส่วนระหว่างบรรทัด ก็ใช่ว่าจะไม่จริงไปเสียทั้งหมดนะครับ แค่บริบทโดยรวม มัน mislead ไปหน่อย
Lactose, we need to talk: The drama behind dairy’s hidden sugar
Cue the violins—it’s the classic love story with a tragic twist: us and dairy. We crave it, we drizzle it, we melt it, we scoop it. But hidden beneath that creamy, dreamy goodness? A troublemaker called lactose.
It might sound harmless, but for a lot of us, lactose is the culprit behind dairy’s not-so-pleasant side effects. In fact, the majority of the world’s population struggles to digest it properly.
So why do we keep chugging cow’s milk like it’s the elixir of life? And how did dairy become such a staple in our diets?
Grab your favorite cheese alternative (might we suggest Frischhain?) and join us for a deep dive into the world of lactose—what it is, why it matters, and how we are stepping in with our animal-free cheese to save the day.
“In a way, being able to chug a glass of milk without consequences is actually a genetic anomaly—one that we pretty much engineered ourselves over thousands of years.” The inside scoop: What’s LActose? Let’s start with the basics. Lactose is the natural sugar found in dairy milk—a built-in sweetener, if you will. But here’s the twist: your body needs a special enzyme called lactase to break it down. Without enough lactase, lactose turns into the life of the digestion-party you didn’t RSVP to: bloating, cramps, and a whole lot of regret.
As infants, our bodies produce plenty of lactase to digest breast milk. But for most of us, that enzyme naturally switches off once we grow into adulthood. In fact, until just a few thousand years ago, lactose intolerance (or “lactase nonpersistence”) was the norm for all adults.
Lactose Tolerance: A genetic Mutation Still today, nearly 70% of the global population are actually lactose intolerant—so, a heck of a lot of people. In certain regions, like East Asia and Africa, that number shoots up to almost 100%. But then, there’s a select few of us who can drink dairy milk without any drama. How’s that possible?
Well, here’s where it gets interesting. The ability to digest lactose as adults—also known as “lactase persistence”—isn’t evenly spread across the globe. Instead, it’s much more common in certain populations—specifically, those with a long history of dairying. Over 10,000 years ago, some humans began herding cows and drinking their milk, eventually triggering a genetic mutation that allowed them to keep producing lactase into adulthood. This trait is especially common in Northern Europe, for instance in Scandinavia and the Netherlands, where dairy farming has been a way of life for millennia.
It may sound weird, but essentially, some populations forced their own evolution by consuming a whole lot of dairy. That’s right. In a way, being able to chug a glass of milk without consequences is actually a genetic anomaly—one that we pretty much engineered ourselves over thousands of years.
The Dairy dilemma: why drink milk from cows? When you really stop and think about it, the need for this genetic mutation kind of makes sense—because, well, we’re not baby cows.
Just like human breast milk is designed to nourish human babies, cow’s milk is specifically made to take a tiny calf and turn it into a full-grown, 500-kilo cow—fast. It’s packed with nutrients meant to help calves double their birth weight in just a couple of months and pack on hundreds of kilos in their first year.
And yet, here we are, well past weaning age, still reaching for a glass of milk—and not just any milk, but milk from an entirely different species. Yeah… kinda weird, huh?
Wait… Do we even need Dairy milk? Remember those food pyramids we all grew up with—the ones that taught us that milk = calcium = strong bones? Well, here’s the interesting part: while we’ve been led to believe that dairy is the ultimate source of calcium, we can actually absorb up to twice as much calcium from leafy greens like kale and bok choy or from broccoli than from milk. Plus, other plant-based sources like firm tofu, fortified plant milks, and fortified juices have plenty of calcium, too.
And here’s the real kicker: more milk doesn’t always mean stronger bones. In fact, several recent studies suggest that high dairy consumption may actually increase the risk of fractures—especially in women. Who saw that coming?
Oh, and while we were all chugging milk to “build strong bones,” no one mentioned the extra ingredients tagging along—cholesterol, antibiotics, growth hormones… and who knows what else.
Some not-so-lovely side effects Alright, let’s get real for a moment. Dairy isn’t just a digestion bummer for many—it can be linked to serious health risks:
Heart Disease & High Cholesterol: Dairy is loaded with saturated fat, contributing to heart disease, type 2 diabetes, and even Alzheimer’s. Increased Cancer Risk: High dairy intake has been tied to higher risks of liver, breast, ovarian, and prostate cancers. Skin Woes: Acne, eczema, and premature aging can be unwelcome side effects of dairy consumption. Dairy has been marketed as a universal health food for decades, yet its consumption patterns have been shaped more by industry influence than genuine nutritional necessity. Lactose intolerance isn’t a niche issue—it’s a reminder that our dietary norms are far from one-size-fits-all.
Beyond lactose: The ripple effects of dairy But avoiding dairy isn’t just about avoiding an upset stomach—it’s about the planet and the animals, too. Dairy farming uses a staggering amount of water and land, and the industry is a huge contributor to greenhouse gas emissions. Not to mention, billions of cows suffer day in, day out, just so we can drink their milk.
And, while we’re at it, let’s bust a myth real quick. That comforting little story about how somehow, we’re “doing cows a favor” by milking them constantly—because otherwise, they’d explode or something? Well…that’s not exactly how it works. Like humans, cows don’t just produce milk on command. They only lactate after giving birth, and in the dairy industry, that’s usually after forcible artificial insemination. Mother and baby are separated almost immediately, and the male calves? They’re either sent to the veal industry or killed right away as surplus.
Cows aren’t built to be milked non-stop, and the constant milking can cause serious health problems, like mastitis (a painful udder infection), lameness, and other injuries.
So yeah—not exactly the family-friendly scenes you might imagine.
“Our mission goes beyond creating tasty alternatives—we’re envisioning a future where indulgence doesn’t come at the expense of animals or the planet.” The frischhain twist: animal-free, lactose-free, problem-free Let’s face it: traditional dairy has a lot of baggage. But breaking up with lactose doesn’t mean giving up on cheese*alternatives. That’s where we come in.
Our animal-free cheese is crafted without cows, using cutting-edge microfermentation to produce Koji protein—closely resembling traditional whey proteins. The result? Delicious cheese*alternatives that’s better for your tummy, your health, and the planet.
No more bloating. No more stomach aches. Just cheesy*alternative goodness—guilt-free.
What’s more, each pack of our cream cheese alternative Frischhain packs 10.9g of protein, saves 1.2kg of CO2 emissions, and uses far less water and land. If that’s not reason enough to give it a go, we’re not sure what is!
why cutting down on dairy is a win for everyone Look, even if you’re not lactose intolerant, switching to animal-free dairy has major perks:
Happy Digestion: Dairy-free options make digestion smoother and help prevent bloating, discomfort, and even energy crashes. Better Skin & Hormones: Going dairy-free can improve skin clarity, reduce inflammation, and balance hormones. Planet-Friendly: Ditching dairy helps reduce excessive water use, land destruction, and greenhouse gas emissions. It’s an easy way to reduce your carbon footprint. Cruelty-Free: Supporting dairy alternatives means less harm to animals, especially the billions of cows in factory farms the future of dairy: diverse, delicious, and dairy-free One of the most exciting aspects of shifting away from traditional dairy is the sheer diversity of alternatives. From fermented nut cheeses to innovative proteins made with micro fermentation, the industry is moving beyond simple substitutions and into entirely new taste and texture experiences. Lactose-free options have never been more delicious or more readily available. And the best part? They’re made for humans, not cows.
Our mission goes beyond creating tasty alternatives—we’re envisioning a future where indulgence doesn’t come at the expense of animals or the planet. So, whether you’re lactose-intolerant, eco-conscious, or just obsessed with really good cheesealternatives, why not give our cow-free cheesealternative a try? The future of dairy is here—and it’s deliciously dairy-free.
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ e2c72a5a:bfacb2ee
2025-05-15 00:57:01
@ e2c72a5a:bfacb2ee
2025-05-15 00:57:01gm, just zap on AFK using Starknet cross-swap ;)
MVP here but new version is coming https://afk-community.xyz
-
 @ 119356ac:740a8b90
2025-05-14 23:08:09
@ 119356ac:740a8b90
2025-05-14 23:08:09► Video Tools
- 🌐 Digital Video Intro - Digital Video Guides / Resources
- ↪️ AI Video Generators
- ⭐ Reincubate Camo - Use Any Camera as Webcam
- Deep-Live-Cam, Rope, SimSwap or Roop - Video Face Swap Tools
- VideoHelp Forum - All Things Media / Video
- ICAT - Video Quality Comparison & Analysis Tool
- videoduplicatefinder - Duplicate Video Finder
- VHS Decode - VHS Decoder
- VidClue - Short Form Video Inspiration
▷ Disc Utilities
- ImgBurn, DVDStyler, DeepBurner or Alcohol Soft - CD / DVD Burning
- MakeMKV - Create MKV From Blu-ray / DVD / Beta Keys
- VidCoder or DVDDecrypter - DVD / Blu-ray Ripping
- DGDemux - Blu-Ray/UHD Disk Demuxer
- PgcDemux - DVD Disk Demuxer
- BatchGuy - Blu-Ray Ripping
▷ Video File Hosts
- Note - Most file hosts remove files after inactivity, while some delete them regardless. Check each host if you're concerned about file expiry.
- ⭐ DoodStream - 5GB / 60 Days / Account Required
- ⭐ Litterbox - 1GB / 3 Days
- ⭐ Catbox - 200MB / Forever / Allows Hotlinking
- ⭐ Gofile - 100GB Monthly / 10 Days
- ⭐ Send.now - Unlimited / 30 Days
- Files.vc - Unlimited / 10GB / Forever / Discord
- VOE - Unlimited / 60 Days / 720p / Account Required
- MixDrop - Unlimited / 60 Days / 720p / Account Required
- FEX.NET - 100GB / 10GB Guest / 7 Days
- FileMoon, 2, 3 - 50GB / 40TB per account / Forever / Account Required
- Hexupload or AnonTransfer - 15GB / 30 Days
- Fastupload.io - 10GB / 30 Days (60 Days with Account)
- Vidoza - 15GB / 15 Days / Account Required
- Streamtape - 15GB / Account Required / .to
- Dubz - 100MB / Forever
- EarnVids
- Streamable - 250MB / 2 Days (90 Days with Account)
- uguu - 128MB / 3 Hours
- webmshare - WebM & GIF Hosting / 20MB / Forever
- Videy - 100MB / MP4 Only
▷ Screen Recording
- ⭐ OBS
- gifcap - Turn Screencasts into GIFs / GitHub
- Shinobi - Network Video Recorder
- MythTV - Digital Video Recorder (DVR)
- tldv or ZoomRec - Record Google Meets / Zoom Calls
- FFmpeg / Tools
- Vileo
- ShareX
- Screen Recorder
- vokoscreenNG
- Cap / GitHub
- Shar.ec - Online
- ScreenREC - Online
- ScreenRecorder.me - Online
- KazCap - Online
- RecordScreen - Online
- Google Screen Recorder - Online
▷ Processing / Encoding
- ⭐ HandBrake - Video Encoding Software / Guide
- ⭐ FFmpeg - Multimedia Processors / Converters / Tools
- ⭐ Shutter Encoder - Video Encoding Software / GitHub
- ⭐ MKVToolNix - MKV Editing Tools
- ⭐ archived-things, The Encoding Guide or Silentaperture - Video Encoding Guides
- ⭐ Disc Rip - Disc Ripping Guide / Mirror
- ⭐ Basics to the Art of Remuxing - Learn How to Remux Videos
- DDVT - Dolby Vision RPU Demuxing / Injecting / Editing
- MKV Muxing Batch GUI - Mux Videos
- staxrip - Video Encoding / Contact Sheet + Thumbnails Creator
- IFME - Video Encoding
- XMedia Recode - Video Conversion
- FastFlix - Video Conversion / GitHub
- NEAV1E or Av1an - AV1 Encoding
- Winnydows - Video Conversion Software
- sickbeard_mp4_automator - Automate Video Processing
- Seven Converter - Video Conversion / GitHub
- nmkoder - Media Encoding / Muxing
- selur - Video Encoding
- vvenc, vvdec or VVCEasy - VVC Encode / Decode
- Ingex - Tapeless (Uncompressed) Recording / Digital Tape Converter
▷ Online Processing
- Compress Video Online - Compress / Unlimited
- 8mb.video - Compress / 2GB
- autocompressor - Compress / 2GB
- Rotato - Compress / 2GB
- VideoSmaller - Compress / 500MB
- YouCompress - Compress / 500MB
- MP4Compress - Compress / 500MB
- VERT - Converter / Discord / GitHub
- Video Express Converter
- VideoConverter - Converter
- Restream Tools - Converter
▷ FFmpeg Tools
- FFmpeg-Builds or media-autobuild_suite - Autobuild Tools
- ffmpeg-web - FFmpeg Web App / GitHub
- FFmpeg Libav or ffmprovisr - FFmpeg Guides
- ASM Lessons - FFmpeg Assembly Language Lessons
- FFmpeg Cheat Sheet, FFmpeg Commander or FFmpeg Buddy - Command Lists
- WebMConverter - WebM Converter
- PureMPV - Info Copy Tool
- ffmpeg.lav - Preview Filters
- LLmpeg or idli - AI Commands
- FFmpeg Batch - Bulk Conversion Tools
▷ Live Streaming
- 🌐 Awesome Streaming or StreamerFreebies - Live Streaming Resources
- ⭐ OBS - Live Stream Manager
- ⭐ OBS Tools - Virtual Cam / Tweaks / Effects / Keyboard Visualiser / Background Remover / Web App / Phone Controller / Dock Layouts / WebRTC Server / Plugin Updater / Guide
- Stream Elements - Streaming Service Manager
- Streamlabs-OBS - Live Stream Manager
- StreamLabs - Live Stream Manager
- Restream - Live Stream Manager
- FBX - Live Stream Manager
- XSplit - Live Stream Manager
- TwitchChat - Live Stream Manager / Discord
- VDO Ninja - Live Stream Colab Tool
- LiveStreamDVR / Display Chat - Live Stream Recorders
- NVIDIA Broadcast - Stream Audio / Video Enhancer
- Owncast or Restreamer - Self-Hosted Live Streaming
- WDFlat - Stream Elements
- Twelve47Studios - Stream Overlays
- Strem - Stream Automation
- ppInk, glnk, Annotate Screen or Live Draw - Screen Annotation
- Amuse or Songify - Now Playing Overlays
- StreamPi or ODeck - ElGato Streamdeck Alternatives
- real-url - Copy Live Stream URLs
- Chat-Downloader - Retrieve Chat Messages from Livestreams
▷ VTuber Tools
- 🌐 Runa's Archive - VTuber Resources / Discord
- Best VTuber - VTuber Resources
- VTResources - VTuber Resources
- VTuber Assets - VTuber Resources
- VTuber Kit - VTuber App
- Inochi2D - VTuber App / Discord
- Vtube Studio - VTuber App
- Kalidoface 3D, VRoid, Animaze or TransTube - VTuber Characters
- avatarify-python or veadotube - Video Call Avatars
- VTuberized Logos - VTuber Style Logos
▷ Subtitle Tools
▷ Linux Video Tools
▷ Mac Video Tools
► Video Players
- 🌐 Awesome Video - Video Streaming Resources
- 🌐 Video Help - Video Player Index
- ⭐ MPC-HC, MPC-QT or MPC-BE - Video Player / YT-DL Support
- ⭐ MPV - Video Player / Frontends
- ⭐ VLC - Video Player
- Screenbox - Video Player
- AVPlayer, ICAT or GridPlayer - Multi-Video Players
- SPlayer - Video Player with Smart Translation
- PotPlayer - Video Player / Twitch Addon / YouTube Addon
- ImPlay - Video Player
- SMPlayer / 2 - Video Player / YouTube
- uView - Video Player
- Rise Media Player - Video Player
- Flyleaf - Video Player
- MoonPlayer - Video Player
- KikoPlay - Video Player
- Plyr - Online HTML5, YouTube and Vimeo Player / GitHub
- PiP-Tool - Use Picture-in-Picture on All Videos
- PlayVideo - Google Drive Video Player
- MotionMonkey - Stream Online Videos in Player
- StreamLink - Extract Videos from Sites to Players / Twitch Adblock / GitHub
- Hohoema - Nico Nico Video Player
- polsy.org.uk - Alt Players for Video Sites
▷ Stream Sync
- ⭐ SyncPlay - App
- ⭐ Watch2Gether - Online Player
- ⭐ SyncWatch - Online Extension
- ⭐ Kosmi - Online Player
- ⭐ WatchParty - Online / Virtual Browser
- ⭐ neko / GitHub - Docker Virtual Browser
- HyperBeam / VIP - Virtual Computer Embed
- Trast, OpenTogetherTube, TurtleTV or twoseven - Online Player
- bear.cat - Online Virtual Machine / Allows NSFW
- Metastream - Online Extension / Discord / GitHub / X
- Caracal Club - Online Video Player
- CyTube - Online Video Player
- VideoTogether - App
- baked.live - Online Video Player
- Rave.io - Online Extension
- MovieNight / Discord - Docker
- Kast - Screen Share
- Screen Share Party - Online Screen Share
▷ MPV Tools
- ↪️ MPV Shaders
- MPV Config Guide, 2, 3
- ModernX, tethys or uosc - Alt User Interfaces
- Simple MPV WebUI - WebUI Controller
- MPV Context Menu
- MPV Scripts - Userscripts
- VideoClip, 2 - Clip Tool
- MPV WebM - WebM Tool
- Play With MPV or ff2mpv - Open Videos with MPV
- MPV WebTorrent Hook - Torrent Streaming
- AutoSubSync MPV - Sub Sync
- MPV SponsorBlock, 2 - SponsorBlock for MPV
- ThumbFast - MPV Thumbnails
▷ VLC Tools
- 🌐 Awesome VLC - VLC Resources
- VLSub - Sub Downloader
- VLC Skin - VLC Skins
- VLC Slow Seek Fix
► Media Servers
- 🌐 Auto Download Tool Index
- ⭐ Jellyfin - Media Server
- ⭐ Kodi - Media Server
- TRaSH Guides / Discord or The Complete Guide - Server Setup Guides
- Self-hosted Anime - Anime Server Setup Guides
- Prowlarr, FlexGet or /r/softwarr - Autodownload Tools
- Organizr, Reiverr or Homarr - Media Server Managers
- Fixarr - Media Server File Renamer
- HTPC Download Box - Media Server Automation
- Emby - Media Server
- Plex - Media Server
- Universal Media Server - Media Server
- OSMC - Media Server
- Kawaii-Player - Media Server
- Streama - Media Server
- Gerbera - Media Server
- Homehost - Media Server
- Dim - Media Server
- Kyoo - Media Server
- WatchIt / GitHub / Discord - Media Server
- SimpleDLNA - Media Server
- Chocolate - Media Server
- Media-Hoarder - Media Catalog Frontend
- Seanime - Anime Server
- Frames - Google Drive Server
- HTPC - Home Theater PC guides / Subreddit
- MSX - Web App
- ErsatzTV or dizqueTV - Live Channel Media Servers
- YTDL-Sub - Add YouTube Channels to Media Servers / GitHub
- xTeVe - Plex / Emby M3U Proxy
- Ombi - Plex / Emby User Request Management
▷ Plex Tools
- Reddit Guide - Plex Setup Guides
- Tautulli - Server Monitor / Note
- SuperPlex - Plex Plugins
- Kitana - Plugin Frontend
- Plex Ripper - Merge Plex Libraries w/ Your Own
- PlexDrive or mergerfs - Mount Google Drive
- SyncLounce - Media Sync
- PseudoTV - Create TV Channels
- Overseerr - User Requests / IMDb Extension
- Pasta Tool - Audio / Sub Changer
▷ Jellyfin Tools
- 🌐 Awesome Jellyfin - Jellyfin Resources
- ⭐ Blink, Fladder or jellyfin-media-player - Desktop Clients
- /r/JellyfinShare - Jellyfin Server Sharing
- Jellyfin Forum - Official Jellyfin Forum
- Jellyfin Vue - Jellyfin Web Client
- Jellyfin "arr" Setup Guide
- Jellyfin Customization Guide
- Jellyfin Themes
- Jellyseerr - User Requests
- Jellyfin RPC - Jellyfin Discord Rich Presence
▷ Kodi Tools
- ⭐ Elementum - Torrent Streaming / Trakt Sync / Similar to Stremio + Torrentio
- EverythingKodi - Kodi Addon Tutorials
- Kodi Builds Chart
- /r/Addons4Kodi / Tracker / Trending - Kodi Addons
- Kodi Skins or WIP Skins - Kodi Skins
- Synko - Kodi Stream Sync
- Plex Kodi Connect or plex-for-kodi - Plex for Kodi
- quasar - Torrent Plugin
- IPTV Client
- Simkl - Media Tracker
- tinyMediaManager or MediaElch - Media Collection Managers
► Video Download
- ↪️ YouTube Video Downloaders
- ↪️ Twitch Video Downloaders
- ↪️ Download Managers
- ⭐ yt-dlp or YTDL-PATCHED - Multi-Site / Commands / Zoom Fix / Discord
- ⭐ cobalt - Multi-Site / Online / Instances / Playlist Support, 2
- ⭐ 9xbuddy, 2, 3 - Multi-Site / Online
- ⭐ Download Helper, FetchV or MPMux - Extensions
- CD(R)M-Project - DRM Tools / Discord
- VideoFK - Multi-Site / Online
- you-get - Multi-Site / CLI
- Hitomi Downloader - Multi-Site / Software
- SCrawler - Multi-Site / Software / Discord
- Musvkrobot - Multi-Site / Telegram Bot
- myfaveTT, SnapTik or tiktok-to-ytdlp - TikTok
- Threads Downloader - Threads
- Piner - Pinterest / Online
- hls-downloader, hls extension or hlsloader - HLS Downloaders
- GetWVKeys - Send Widevine Requests / GitHub
► Video Editing
- ⭐ /r/VideoEditing - Video Editing Subreddit / Wiki
- ⭐ Eyecandy - Visual Technique Examples
- ⭐ Waifu2x GUI, Video2x, Enhancr, Lossless Scaling or Dandere2x - Video Upscaling
- Codecs and Containers - Info on Codecs & Containers
- ALF FreeWare VideoCODECs, Codec Guide or Free-Codecs - Video Codec Collections
- VideoHelp Forum - Video Editing Forums
▷ Video Editors
- ⭐ LosslessCut - Video Editor
- ⭐ kdenlive - Video Editor / GitHub
- ⭐ DaVinci Resolve - Video Editor / Sign-Up Required
- ⭐ Shotcut - Video Editor
- Auto-Editor - CLI Editor
- MoviePy - Python Editor
- Webm Generator - Webm Editor
- avisynth or VapourSynth - Video Processors
- Source Filmmaker - Steam Movie-Making Tool / Resources
- OpenRV - Image / Sequence Playback Review
- Remotion - Video Editor
- Olive - Video Editor
- EZVid - Video Editor
- OpenShot - Video Editor
- Lightworks - Video Editor
- VSDC - Video Editor
- Pitivi - Video Editor
- Visla - Video Editor
- Windows Movie Maker, 2, 3 - Video Editor
- Avidemux - Cut / Filter / Encode
- suckless-cut or vidcutter - Cut / Trim Videos
- Opus - Clip Creator
- Kurku or FreeMoCap - Motion Tracking Tools
- VSeeFace - Face / Hand Tracking VRM
▷ Online Editors
- ⭐ wide.video - Discord
- ⭐ Pikimov - Use Edge or Chrome
- ⭐ Mastershot - Sign-Up Required
- VideoToolbox - Sign-Up Required
- VideoInu - Works Offline
- Panzoid
- vidmix
- Video Cutter
- Omniclip - GitHub / Discord
- Vididoo - Multitool
- VideoCandy - Multitool
- Video2Edit - Multitool
- Crop Video - Crop Videos
- LoopVid - Loop Videos
- Crossfade - Video / Audio Crossfading
- VidLouder - Increase Video Volume
- Convert2Video - Image / Audio to Video
▷ Video Enhancement / Effects
- Video Enhance AI - Video Enhancement Tool / Search "Topaz" on LR
- Gyroflow - Video Stabilization / GitHub
- Flowframes / Beta or SVP / Guide - Video Interpolation / Increase FPS
- VideoColorizerColab - Video Colorization Colab
- OpenColorIO - Video Color Manager
- FreshLUTs - Free LUTs (Color Filters)
- blur or Smoothie - Add Motion Blur to Videos / Tutorial
- ProPainter - Video Inpainting
▷ VFX Sites
- FootageCrate
- FreeVideoEffect
- VideoCoPilot
- VFXmed
- Team V.R releases
- flex_cg_vfx
- VFXLoot
- Download Pirate - Use Adblock / Avoid Fake Download Buttons / Discord
- ShareAE - After Effects
- HunterAE - After Effects
- Visual Effects Pack - After Effects
- AERiver - After Effects
- AEDownloadPro - After Effects
- Intro HD - After Effects
▷ Animation Tools
- 🌐 Creator Resources - Art & Animation Resource Index
- ⭐ Unreal Engine, MoonRay, cgsoftbox, SketchUp or Twinmotion - 3D Creation Tools
- ⭐ Immersity AI - 2D Image to 3D Animation Tool
- OpenToonz, Wick Editor, Clipnote Studio or Pencil2D - Animation Tools
- Animaker - Animated Video Creator
- 3DThis - 3D Animation Tools
- Mega Scans - 3D Scans
- Mixer - 3D Texture Creation Tool
- PlanetSide - CG Environment Generator
- cgplugdump - CG Software Plugins
- Physically Based - RGB Values of Elements
- AnimeEffects, enve, Cavalry, TupiTube or Synfig - 2D Animation Tools
- ScribbleDiffusion - Turn Doodles into Artwork
- MonsterMash - Sketch-Based Modeling & Animation Tool
- Storyboarder - Quickly Visualize & Test Animations / GitHub
- LuxCoreRender - Rendering Engine
- RenderChan - 2D Animation Render Manager
- Mandelbulber or FragM - Fractal Rendering Software / 3D
- JWildfire, IFSRenderer or Fractorium - Flame Fractal Rendering Software
- BestSnip, Sketch Machine, Plask or Rive - Online Animation Tools
- Glaxnimate or Trangram - Vector Animation Tools
- LibreSprite, GraphicsGale, Pixel Compresor, JPixel, Aseprite / Guide or SpookyGhost - Pixel Art Animation Tools
- Spritesheet Generator - Spritesheet Generator / Gitea
- Animated Drawings, FAIR Animated Drawings or MotorPen - Animate Drawings
- FlipAnim - Create Animated Flipbooks
- Viggle / Discord or Picrew - Animated Character Creators
- Mixamo or Cascadeur - 3D Character Animation Tools
- MMHuman3D - 3D Human Model Creator
- Talking Face Avatar - Talking Avatar Generator
- Blender Open Movies - CGI Assets
▷ Stock Videos
- 🌐 Awesome Stock Resources or CuteStockFootage - Stock Video Indexes
- Pexels - Stock Videos
- 4K Media - 4K Stock Videos
- Dareful - 4K Stock Videos
- Monzoom - 4K Stock Videos
- BeachFrontBroll - Stock Videos
- Videvo - Stock Videos
- veed.io - Stock Videos
- VidsPlay - Stock Videos
- MitchMartinez - Stock Videos
- MixKit - Stock Videos
- ineedfx - Stock Videos
- MotionPlaces - Worldwide Stock Videos
- DroneStock - Drone Video Footage
- MovieTools - Video Loops
-
 @ 119356ac:740a8b90
2025-05-14 23:06:55
@ 119356ac:740a8b90
2025-05-14 23:06:55► Text Tools
- ↪️ Image to Text
- ↪️ Text to Speech
- ↪️ Study / Research
- ↪️ Data Visualization
- ⭐ TextCleanr, Text Mechanic, TextFixer, OnlineTextTools, Convert Case, TextCleaner, SortMyList or The Alphabetizer - Organize / Format Text
- OpenPaper, papis, PaperMerge, Paperless-ngx / Doc Analyzer or DataShare - Document Managers
- SmartDoc - Document Analyzer
- diffr, Diffchecker, TextCompare, Text-Compare, OnlineTextCompare, CompareText or DiffNow - Compare Text
- Count Duplicates or DuplicateWord - Count / Remove Duplicates in a List
- WindowTextExtractor - Extract Text From Any Window
- Textify - Copy Text from Any Dialog
- BeefText - Text Substitution Tool
- Scanner or NAPS2 - Scanner Apps / GitHub
- Calligrapher.ai, Text to Handwriting, texttohandwriting or HandWrittner - Text to Handwriting Converters
- StegCloak - Hide Messages in Text
- telescopictext - Write Text Within Text
- quipqiup or dCode - Cryptogram Solvers
- DocuSeal - Free Document Signing
- TemplateLab or FreePrintables - Free Document Templates
▷ Pastebins
- 🌐 PrivateBin Instances
- ⭐ Rentry, 2 - Markdown Support / CLI / Styling
- ⭐ GitHub Gists - Multi-Syntax / Account Needed
- ⭐ pastes.dev - Multi-Syntax / Markdown Support / GitHub
- ⭐ PrivateBin, 2 - Markdown Support / Syntax Highlighting / GitHub
- ⭐ Katbin - Plain Text / GitHub
- snowbin, 2 - Markdown Support / GitHub
- Text.is - Markdown Support / Rentry Clone
- Stellular, 2, 3 - Markdown Support
- bpa.st - Multi-Syntax / Markdown Support
- dpaste - Multi-Syntax / Markdown Support / GitHub
- cryptgeon - Single View / Plain Text / GitHub
- Paste.ee - Multi-Syntax / Markdown Support
- pst.moe - Multi-Syntax / Markdown Support / Source
- dpaste.com - Multi-Syntax / Markdown Support
- Pastebin.com - Multi-Syntax
- pastebin.pl - Multi-Syntax
- CentOS Pastebin - Multi-Syntax
- Microbin - Multi-Syntax
- snippet.host - Multi-Syntax
- ProtectedText - Multi-Tab
- bin - Minimal Pastebin
- txt.fyi - Markdown Pastebin
- MarkdownPastebin - Markdown Support
- Sparked Paste - Plain Text / Syntax Highlighting
- Riseup Pad - WYSIWYG Pastebin
- WriteXO - WYSIWYG Pastebin
▷ Translators
- Note - Chatbots like ChatGPT and Claude can also translate text, and are sometimes better than the ones listed below.
- ⭐ DeepLX or DeepL - AI-Based
- ⭐ Kagi Translate, Google Translate / Extension, Lingva Translate or GTranslate / API - Translation Sites
- ⭐ /r/Translator - Translation Request Community
- ⭐ Translate Web Pages - Browser Extension
- Argos - Translation Apps
- Translate Shell - Translation CLI / GitHub
- OnlineDocTranslator - Document Translator
- Matecat - Online Translation Editor
- LingoJam - Create Translator
- Renpy Translator or Renpy Editor - Ren'py Automatic Translator / Editor
- Translator++ - Automatic Translator / Editor
- Eazypo or Poedit - Translation Editor
- OmegaT - Translation Memory Tool
- Morsecode World or MorseDecoder - Morse Code / Binary Translators
- Emojify - Emojify Text
- Simple Translate - Browser Extension
- Linguist Translator - Browser Extension
- ImTranslator - Browser Extension
- Papago
- Libretranslate / 2
- ImmersiveTranslate / Extension
- Translate.com
- MyMemory
- Nice Translator
- Yandex Translator
- Bing Translator
- Reverso
- babelfish
- translation2
- collinsdictionary
- translatedict
- Translator.eu
- Textractor - Game / Visual Novel Translator
▷ Audio Transcription
- 🌐 ASR Leaderboard - Speech to Text Leaderboard
- Whisper - Audio Transcription / WebUI, 2
- mp4grep - MP4 File Transcription Tool
- SpeechTexter, VoiceToText, Dictation, oTranscribe or TalkTyper - Browser-Based Speech-To-Text Tools
- Revoldiv or Turboscribe - AI-Based Transcriptions
- Vibe - Audio Transcription Software
- Buzz - Audio Transcription Tool
- WhisperX - Audio Transcription Tool
- SpeechNotes - Speech Recognition Notes App
- LilySpeech - Fast Voice-To-Text Software
- VoiceNotebook - Speech Transcription Notebook
▷ Encode / Decode
- 🌐 DecodeUnicode - Unicode Decoding Database
- ⭐ CyberChef - Encode / Decode Text / GitHub
- ⭐ Base64 Decode or Base64 Editor - Encode / Decode Base64
- ⭐ Auto Decoder - Auto-Decode B64 Links on Pastebins
- Ciphey - Automated Decryption Tool
- Universal Encoding Tool - Encode / Convert Text
- cryptii or DenCode - Text / URL Encoding
- Coder - Text / File / URL Encoding
- Online Tools - Text / URL Encoding and Decoding
- URL Decode / Encode - URL Encoding / Decoding
- Base64 Repair - Fix Broken Base64
- Base64 Extensions - Chrome, 2, 3 / Firefox
▷ Grammar Check
- Note - Most chatbots in the AI section can also check grammar.
- ⭐ LanguageTool
- Writing Tools - Desktop App
- DeepL Write
- QuillBot
- Scribens
- EditGPT - Sign-Up Required
- Grammarly - Sign-Up Required / Extension
- ProWritingAid - Sign-Up Required
- Outwrite - Sign-Up Required
▷ Text Rephrasing
- ⭐ QuillBot AI or Rewritify - AI-Enhanced Text Rephrasing
- ⭐ Paraphrasetool or Rephrasely - AI Text Rephrasing / Generation
- ⭐ Goblin.tools - Transform Text with Spiciness Levels
- Paraphraser - Multilingual Text Rephrasing
- Paraphrase-Online, Paraphrasingtool, Henshu or WriteFull - Versatile Text Rewriting
▷ Emoji Indexes
- ⭐ Emojipedia, EmojiDB, Slackmojis, Emoji Picker or EmojiBatch - Emoji Indexes
- Emoji Engine - Multilingual Emoji Search
- winMoji - Emoji Managers
- EmojiRequests - Custom User-Made Emojis
- Cult of the Party Parrot - Party Parrot Emojis
- Pepe Server Archive - Pepe Emojis
▷ Unicode Characters
- ⭐ Amp What
- CopyChar
- Unicode Table
- Unicode Explorer
- Character Map
- Unifoundry
- Cool Symbol
- emotes.io, CuteSymbols, 2 or GetSymbol / 2 - Copy Unicode Emotes
▷ Typing Lessons
- ⭐ Monkeytype - Customizable Typing Tests / Discord / GitHub
- Typing Guide - In-Depth Typing Guide
- Typing.io - Typing Practice for Programming / Sign-Up Required
- Typ.ing, Typings or typing.works - Typing Tests
- keybr - Typing Practice
- CyberType - Typing Practice
- Typing.com - Typing Lessons
- Typing Club - Touch Typing Lessons
- typing.academy - Typing Lessons / Requires JavaScript Enabled
- TypeRacer, ZType, TypeRush or ARRRType - Typing Games
- NGram Type, KeyZen MAB or Keyzen Colmak - Touch Typing Tests
- TypeLit.io or Entertrained - Book Typing Tests
- Colemak Academy - Alt / Custom Keyboard Tests
- TypingStudy or TypeFast - Multilingual Typing Tests
- 10fastfingers - Typing Competitions
► Text Editors
- 🌐 List of Text Editors - Text Editor / Notepad Index
- ↪️ Android Text Editor
- ↪️ Code Editors / IDEs
- ↪️ Markdown Editors
- ⭐ Notepad++ / GitHub or NotepadNext - Notepad & Code Editor / Markdown
- EncryptPad - Encrypted Text Editor / GitHub
- Notepads - Text Editor / GitHub
- FastNotes - Text Editor / GitHub
- Kompad - Text Editor / GitHub
- Sublime Text - Text Editor / Patcher / Package Manager
- Zim Wiki - Wiki Text Editor
- tomboy-ng - TomBoy-Based Text Editor
▷ Note-Taking
- ↪️ Android Note-Taking
- ⭐ Obsidian - Markdown Note-Taking / Discord
- ⭐ Obsidian Tools - Resources / Publish Notes / Web Clipper / Google Drive Sync / ChatGPT Addon / Guides / Forum
- ⭐ Notion - Note-Taking
- ⭐ Notion Tools - Themes / Templates / Resources, 2 / Guide / Markdown Extractor
- ⭐ Notesnook - Note-Taking / GitHub
- ⭐ AnyType - Note-Taking
- ⭐ Logseq - Outlining
- Mochi Cards or Silicon - Note-Taking / Study Tools
- Flotes - Markdown Note-Taking
- QOwnNotes - Markdown Note-Taking
- AFFiNE - Note-Taking / GitHub
- vNote - Markdown Note-Taking / GitHub
- Tiddly - Info Manager / Desktop
- Trilium - Info Manager
- Org-roam - Info Manager
- Desklamp - Reading / Note-Taking / Highlighting Tool / Guide
- UseMemos - Note-Taking / Discord / GitHub
- Papers.IM - Note-Taking
- Joplin - Note-Taking / Firefox / Chrome / GitHub
- AppFlowy - Note-Taking / GitHub
- MicroPad - Note-Taking
- WriteDown - Note-Taking
- DocMost - Note-Taking
- KeyNote NF - Note-Taking
- SilentNotes - Note-Taking / GitHub
- Google Keep - Simple Notes
- StandardNotes - Encrypted Notes
- Saber - Handwritten Notes
- Butterfly - Handwritten Notes / Discord / GitHub
- Xournal++ - Handwritten Notes / GitHub
- BookStack or Siyuan - Self-Hosted Info Managers
▷ Office Suites
- ↪️ Office Activation / Guide / Custom Install Guide
- ⭐ LibreOffice - FOSS Office Suite
- ⭐ OnlyOffice - FOSS Office Suite
- ⭐ Microsoft Office - Office Suite / Removal Tool / Hot Keys, 2
- Calligra - FOSS Office Suite
- Office365Version - Office 365 Version History
▷ Online Editors
- ⭐ Simplenote - Local / Cloud Saves
- ⭐ Proton Docs - Local / Cloud Saves
- ⭐ takenote - Local Saves
- ⭐ Zen - Local Saves
- Leaflet - Cloud Saves / Customizable / Examples
- Browserpad - Local Saves
- Notepad - Local Saves
- onlinenotepad - Local Saves
- notepad-online.net - Local Saves
- ssavr - Local Saves
- notepad-online.com - Local Saves
- JustNotePad - Local Saves
- PasteePad - Local Saves
- Shrib - Local / Cloud Saves
- MemOnNotepad - Local / Cloud Saves
- Write Box - Local / Cloud Saves
- dDocs - Cloud Saves
- NimbleText - Cloud Saves
- ZippyJot - Cloud Saves
- KiloDoc - Cloud Saves
- TinyList - Cloud Saves
- Edit-Document - Local / Cloud Saves
- TextSlave - Cloud Saves
- GhostText - Cloud Saves
- AnyTextEditor - Cloud Saves
▷ Mind Mapping
- ⭐ Obsidian Canvas
- FreeMind
- Kinopio
- Freeplane
- Mindomo
- Yuque
- MindMapp
- are.na
- Domino
- GitMind
- xTiles
- Capacities
- bubbl
- Heimer
- Cubox
- vym
- markmap - Markdown Mind Mapping / GitHub
- Coggle - Collaborative
- CardSmith - Collaborative Mind Mapping
- Memrey - Collaborative Mind Mapping
- MindMeister - Collaborative Mind Mapping
- Slatebox - Collaborative Mind Mapping
▷ Text / Code Collaboration
- ⭐ Google Docs / HTML Converter
- ⭐ CryptPad
- ⭐ Kludd
- Mattermost
- Codeshare
- HackMD
- Taskade
- Socket
- Whimsical
- Ellipsus
- Etherpad
- SharePad
- Pixso
- FidusWriter
- overleaf
- Rustpad / GitHub
- OnlineInterview.io
▷ Spreadsheet Editors
- 🌐 MTEB Leaderboard - Text Embedding AI Leaderboard
- tad, Tree Sheets, Gnumeric or Quadratic - Spreadsheet Viewers / Editors
- Baserow, Framacalc, EtherCalc, NocoDB or AirTable - Collaborative Spreadsheets
- Jamovi - Statistical Spreadsheets
- Excel Practice Online - Excel Practice / Guides
- Excel Macro Mastery - Excel VBA Guides
- ExcelJet or Excel Functions - Excel Formulas
- Vertex42 - Excel Templates
- Plain Text Table - Text Tables
- EditCSVOnline - Online CSV Editor
- SubjectiveSort - Create Ranked List from CSV
- VisiData - Spreadsheet CLI Editor
- Structifi - Convert Files to Structured Data
- TadViewer - View / Analyze Tabular Data
▷ Writing Tools
- 🌐 Author Stash - Writing Tools / Resources
- ↪️ AI Text Generators
- ⭐ Writer, FocusWriter, Writemonkey, blank.page, Telegra.ph, Aurelius, ZenPen, Write.as, Owri, WriteSpace or WriteNext - Distraction-Free Writing
- ⭐ Manuskript - Writing Organizer / Planner
- ⭐ NovelWriter or Bibisco - Novel Editors
- ⭐ Linked, journaltxt, Gekri, Microsoft Journal, Diarium, Gemlog or jrnl.sh - Journal Apps
- ⭐ ChaoticShiny, Seventh Sanctum, Notebook.ai or WorldAnvil - Fantasy Writing Generators
- Tuesday JS - Visual Novel Editor / GitHub
- RenPy - Visual Novel Editor / GitHub
- Fortelling or Novelist - Novel Plotting / Editing Workspaces
- Infinite Story, Strand, Agora or WriteAlong - Collaborative Writing / Feedback
- LanguageIsAVirus or MDWA - Writing Prompts
- Twinery - Interactive Non-Linear Story Creator
- TextUSM - User Story Map Generator / GitHub
- Blackout Poetry - Blackout Poetry Creator
- Idyll - Create Interactive Essays / GitHub
- STARC, WriteSolo or Celtx - Script / Screen Writing Tools
- Rarebit - Webcomics Template
- Fantasy Name Generators - Fantasy Name Generators
- PolyGlot or VulgarLang - Spoken Language Construction Tools
- How to annotate literally everything - Annotation Tools / Resources
- Label Buddy - Annotation Tool / GitHub
- rNote - Annotation Tool / GitHub
- MonsterWriter - Thesis Writing / Note-Taking
▷ To Do Lists
- ↪️ Android To-Do Apps
- ⭐ Goblin.tools - Automatic Task Breakdown
- ⭐ TickTick / Premium
- ⭐ Super Productivity
- Columns or ChecklistGenerator - Checklists
- YearCompass - New Years Resolution Booklet
- daily.place
- SuperList
- dooit / Extras
- ToDo List / GitHub
- Diry AI
- Fokus
- OpenToDoList
- Microsoft To Do
- NullBoard
- LunaTask
- ToDoZero
- LifeAt
- Tasks
- Taskwarrior
- Vikunja
▷ ASCII Art
- ⭐ TAAG, DeepAA, Kammerl, ASCII Art Studio or ASCII Today - ASCII Art / Text Generators
- REXPaint, Playscii or PabloDraw - ASCII Editors
- ASCII Paint - ASCII Paint Tool
- ascii-art-generator, asciiart, ascii-image-converter, Monospace, ITOA, text-image or ASCII-art-creator - Image to ASCII Art
- Love ASCII, asciiart.eu, EmojiCombos, 16colors, ascii.co or RoySAC - Browse / Copy ASCII Art
- Image to Braille - Convert Images to Braille
- AnsiLove or convert-ascii-to-image - ANSI / ASCII Art to PNG Converters
- lvllvl or Petmate - C64 PETSCII Image Editor
► Fonts
- ⭐ Nerd Fonts - Icon-Rich Developer / Terminal Fonts
- OpenDyslexic - Typeface for Dyslexia
- Typewolf or Typ.io - Trending Website Fonts
- Cava's Pixel Resources - Pixel Fonts
- Oldschool PC Fonts - Oldschool PC Fonts
- FiraCode, Cascadia Code or Maple Font - Monospace Fonts
▷ Open Source / Freeware
- ⭐ FontSource - Open Source
- ⭐ Font Squirrel - Commercial Use
- ⭐ DaFont - Freeware
- ⭐ 1001 Fonts - Freeware
- Modern Fonts Stacks - Collection of CSS System Font Stacks
- Velvetyne - Open Source
- uncut.wtf - Open Source
- Beautiful Web Type - Open Source
- FontRepo - Open Source
- Bunny Fonts - Open Source
- Google Fonts - Commercial Use / Tags / Privacy-Friendly API
- FontShare - Commercial Use
- Fontlot - Freeware
- Fontsly - Freeware
- Fonts4Free - Freeware
- FontSpace - Freeware
- Online Fonts - Freeware
- CDNFonts - Freeware
- Fontesk - Freeware
- FontStruct - Freeware
- iFonts - Freeware
- DownloadFonts - Freeware
- AbstractFonts - Freeware
- FontGet - Freeware
- FreeFontsDownload - Freeware
- Fonts2u - Freeware
- Awwwards - Freeware
- GlukFonts - Freeware
- Iconian - Freeware
▷ Free Fonts
- ⭐ Fonts CSE - Multi-Site Font Search
- ⭐ Font Piracy 101 - Font Download Guide
- ⭐ Font Drives
- ⭐ BeFonts
- Windows Fonts
- Free Fonts Family
- Cufon Fonts
- FontsFree
- DFonts
- Font Spring
- FFonts
- FontsHub
- Font Meme
- FONToMASS
- 1.5_million_fonts
- Mr.E-Fonts
- psd_fonts
- 1001 Free Fonts
► Font Tools
- ⭐ Font Interceptor - Download Fonts from Websites
- ⭐ FontDrop - Analyze Font Files
- ⭐ Adobe Fonts, Font Finder, WhatTheFont, Identifont, WhatFont - Font Identification Tools
- Fonts Ninja - Font Identification Extension
- Unicode Explorer or Compart - Unicode Character Identification
- Transfonter - Create CSS @font-face Kits
- TypeRip - Adobe Font Ripper / GitHub
- FontBase, NexusFont or Font Manager (Linux) - Font Managers
- Colors & Fonts - Typography Tools
- DS-Fusion - AI Typography Generator
- Formito - Typography Logo Maker
- Type Terms - Typography Cheat Sheet
- The Good Line-Height - Typography Scaling Editor
- Font List or So You Need A Typeface 2.0 - Examples of Font Styles
- Type Design Resources or Free Faces - Typeface Resources
▷ Font / Text Generators
- ⭐ FontoGen - Custom AI Font Generator
- ⭐ Make WordArt, FlameText, MakeText, TextGiraffe, Text Pro or CoolText - WordArt Generators
- Polona Typo - Generate WordArt from Book, Poster, & Map Letters
- Text Color Fader - Rainbow Text Generator
- TextDrom, 3DText2GIF or TextStudio - 3D / Animated Text Generators
- Textanim or Space Type Generator - Animated Text Generators
- Batname - Batman (2022) Text Generator
- NFG's Arcade Font Maker or Arcade Font Writer - Arcade Text Generators
- Glitch - Zalgo Text Generator
▷ Font Customization
- ⭐ TypeTrials - Variable Font Playground
- V-Fonts or Phase - Variable Fonts Testers
- enFont or Calligraphr - Custom Font Creators
- Fontjoy - Generate Font Combinations
- FontSprite - FontSprite Editor
- BitFontMaker2 - BitMap Font Editor
- FontEdit, metaflop, MFEKglif, Glyphr Studio, Birdfont, Universal Sans or FontForge - Font / Typeface Editors
▷ Unicode Text Generators
-
 @ 119356ac:740a8b90
2025-05-14 23:03:53
@ 119356ac:740a8b90
2025-05-14 23:03:53► File Tools
- ↪️ File Scanners
- ⭐ Fileinfo, Filext or OpenMyFiles - File Extension Libraries
- ⭐ czkawka or dupeGuru - Duplicate File Finders
- ⭐ Phockup - Organize Photo / Video Files by Date
- UnLock IT or Lock Hunter - File Unlocker / Deleter
- Magika - AI File Content Type Detector
- Icaros - Add Explorer Thumbnails to any Video Format
- Tagging for Windows - Tag-Based File System
- HTTPDirfs or hfs / 2 - HTTP File Systems
- WinBtrfs - Btrfs File System
- mergerfs - Union File System
- filebrowser - Online File Viewer
- WhatsLink - View File Download Metadata
- File-Examples - Dummy File Examples
- OpenHashTab - Compare / Display File Hashes
- Attribute Changer - Edit File & Folder Properties
- TagSpaces - Add Tags to Files and Folders
- SKTimeStamp - Change File Created / Modified Time
- ExtractMetadata or Metadata2Go - Metadata Viewers / Editors
- CUETools - Manupulate .cue Files / GitHub
▷ Download Managers
- ⭐ JDownloader - Download Manager / Debloat / Dark Theme, 2 / Dracula Theme / Apps
- ⭐ IDM - Download Manager
- AB Download Manager - Download Manager / GitHub / Telegram
- Go Speed - Download Manager / Extension / Plugins / GitHub
- aria2 or Persepolis - Terminal Download Manager / GitHub / Download Bot / WebUI, 2
- pyLoad - Lightweight Download Manager
- Hitomi - Multi-Site Media Download Tool
- ArrowDL - Download Manager / GitHub
- FDM - Download Manager / YTDL Addon
- File Centipede - Upload / Download Manager
- DownThemAll - Download Management Extension
- HTTP Downloader - Download Manager for HTTP / FTP / SFTP Protocols / GitHub
▷ Archiving / Compression
- 🌐 SuperCompression - File Compression Resources
- ⭐ NanaZip or 7-Zip - File Archiver
- ⭐ PeaZip - Cross Platform File Archiver
- ⭐ CompactGUI - Transparent Compression
- Fileforums or Encode - Data Compression Forums
- TurboBench - Compression Benchmark
- WinRAR, 2 - File Archiver / Licenses
- Efficient Compression Tool or Minuimus - File Archivers / Optimizers
- ezyZip - Zip Files Online
- unzip-online - Unzip Files Online
- Unrar online - Unrar Files Online
- UPX - Executable File Compressor / GitHub
- lessmsi - .msi Content Extractor / GitHub
▷ File Converters
- 🌐 .to Sites - File Converters Index
- ⭐ File Converter - Convert / Compress Files / GitHub
- ⭐ VERT / Discord / GitHub
- Pandoc - Document Converter
- ConvertCSV - Online CSV Data Conversion
- Encoding Converter - Online File Encoding Converter
- Deark - Decode and Convert Files / GitHub
- text2img - Online NFO Files to Image Converter
- CloudConvert - Convert Files / 1GB
- FreeConvert - File Converter / 1GB
- videoutils - File Converter / 500MB
- Xconvert - File Converter / 400MB
- ConvertFiles - File Converter / 250MB
- Convertio - File Converter / 100MB
- AnyConvert - File Converter / 100MB
- onlineconvertfree - File Converter / 100MB
- MiConv - File Converter / 75MB
- Converter 365 - File Converters / 200MB
- Aconvert - Various Converters / 40MB
- LetsConvert - Image/Audio Converter / 250MB
- Online Convert - Online File Converter
- Zamzar - File Converter / 200MB
- Online Converter - Online Simple Media / Unit Converter
- Convert Town - Online Text / Image Converter
- Docspal - Various Converters / 50MB Image, Documents / 200MB Video, Archive, Audio
- Better Converter - Text-Focused Converters / 10MB
- go4convert - Online Document Converter / 100MB
▷ File Explorers
- ⭐ Files - Customizable File Manager / Use Classic Installer / Discord
- ⭐ Directory Opus - Windows File Manager
- Xplorer / GitHub / Discord, DoubleCMD or muCommander - Cross Platform File Explorers
- Sigma - Modern File Manager for Windows / Linux / GitHub
- ChromaFiler - Column-Based Windows File Manager
- Yazi - Terminal File Explorer / Plugins / GitHub
- One Commander - File Explorer
- Free Commander - File Explorer
- Q-Dir - File Explorer
- Quick Access Popup - File Explorer
- FileExplorer - File Explorer
- FileStash - File Manager / GitHub
- Explorer++ - Lightweight Windows File Manager
- Far Manager - Windows File / Archive Manager
- Total Commander - Shareware Windows File Manager
- Organize - Automated File Manager
- TrayDir - System Tray File Manager
- TablacusExplorer, QTTabBar or Multi Commander - Tab File Managers
- Vifm - Vim-Based File Manager
- WinSetView - Globally Set Explorer Folder Views
▷ File Searching
- ⭐ Everything - File Search Engine
- Recoll / Addon, Spyglass, DocFetcher or Orange - Cross Platform Search Engines
- AnyTXT or FluentSearch - Windows Search Engines
- AstroGrep, grepWin or dnGrep - Windows GUI Grep Utilities
- fselect - SQL-like Search Engine
- fd - User Friendly "find" Alternative
- sist2 - Simple Incremental Search Tool
▷ File Encryption
- ⭐ Cryptomator / GitHub or Tahoe-LAFS / GitHub - Cloud File Encryption
- ⭐ VeraCrypt - Disk Encrypter
- ⭐ Picocrypt - Lightweight File Encrypter
- age - File Encrypter
- gocryptfs - File Encrypter
- Hat - Browser-Based Encrypter
- Kryptor - File Encrypter
▷ File Sync
- ⭐ SyncThing - Cross-Platform File Sync / Tray Support / GitHub
- ⭐ FreeFileSync - Open-Source File Sync
- MyPhoneExplorer, SyncFolder - Phone and Desktop Sync
- allwaysync - File Sync Utility
- Resilio - P2P File Sync
- SmartFTP - FTP File Sync
- rsync - Command-line File Sync / GitHub
- Unison - Bidirectional File Sync
▷ File Backup
- ⭐ Kopia - Encrypted File Backup / GitHub
- ⭐ Rescuezilla or CloneZilla - Disk Image Backup
- FolderClone or Echosync - Folder Clone / Backup
- BackupPC - Networked File Backup
- TeraCopy - File Backup
- restic / GitHub, duplicity or Duplicati - Secure File Backup
- UrBackup - Client / Server File Backup
- AOMEI Backupper - Windows File Backup
- Borg - De-duplicating File Backup
- USBImager - USB Image Backup
- Toucan - Portable File Backup
▷ File Recovery
- ⭐ TestDisk - File Recovery
- PhotoRec - File Recovery
- DMDE - File Recovery
- Windows File Recovery - File Recovery
- MultiPar - Prevent File Corruption / Guide
- ShadowExplorer or ShadowCopyView - Shadow Copy Explorers
▷ Formatting / Deletion
- ⭐ SDelete - File Deletion CLI
- Eraser, File Shredder, Alternate File Shredder, Permadelete or Delapp - File Shredding
- SSuite File Shredder and Burner - File Shredder with Disk Burning
- Low Level Format, nwipe or ShredOS - Complete Hard Drive Erasers
- RED - Remove Empty Directories
▷ Data Automation
- ⭐ Advanced Renamer or Bulk Rename Utility - Bulk Renamers
- FoliCon - Automatic Custom Media Icons / Folders / GitHub
- MediaMonkey - Media Organizer
- MediaInfo - Media File Analysis / Online
- tinyMediaManager or MediaElch - Media Collection Managers
- FileBot - Media File Renaming
- TVRename - TV File Data Automation
- Shoko - Anime File Data Automation
- PowerRename, Szyszka, F2, Ant Renamer or Flut Renamer - Bulk Renamers
► PDF Tools
▷ Online PDF Toolkits
▷ Offline PDF Toolkits
- ⭐ PDFGear
- PDF24
- Foxit / Pro / Warning
- xPDFReader
- PDF Arranger
- PrivatePDF
- PDFBox
- OpenPDF
- Stirling-PDF
▷ PDF Conversion Tools
- Rare2PDF, online2pdf or 2PDFConverter - File to PDF Conversion
- MD2PDF - Markdown to PDF Converter
- PDFconvert - PDF File Converters
- Marker - PDF to Markdown
- PDFCrowd, TailWindPDF or wkhtmltopdf - HTML to PDF / Image Converter
- Issuu - Convert PDF Files to Webpages, Flipbooks, Brochures & More / Downloader, 2
- WebToPDF or Percollate - Webpage to PDF Converters
- Dangerzone - Convert Malicious PDFs to Safe Files / GitHub
▷ PDF Utilities
- PDFGrep or OCRmyPDF - PDF Text Search
- View-only PDF - Download View-Only PDF on Google Drive
- PDFEncrypt - PDF File Encryption
- GraphPaper - PDF Graphs
- Aspose or pdf-unstamper - PDF Watermark Remover
- PDF Fixer - Repair Damaged PDFs
- OpenSign, FalsiScan, JustSignPDF or Adobe Sign - PDF Signature Tools
- Google Drive PDF Downloader - Download Protected Google Drive PDFs
- PDFCoffee - Upload PDF, Word or PowerPoint Files
- PrintFriendly - Printer Formatting Tools
► File Transfer
- ⭐ LocalSend - Desktop / Mobile Transfer / Discord / GitHub
- Photon - Desktop / Mobile Transfer / GitHub
- KDE Connect - Desktop / Mobile Transfer
- Warpinator - Desktop / Mobile Transfer
- Sefirah - Desktop / Mobile Transfer
- QRServ - Desktop / Mobile Transfer / GitHub
- Magic Wormhole - Desktop / Mobile Transfer
- croc - Desktop / Mobile Transfer / GUI
- LANDrop - Desktop / Mobile Transfer
- OnionShare - Share Files Over Tor Network
- FileZilla - FTP Client
- WinSCP - FTP Client
- Wing FTP - FTP Client
- Xlight - FTP Client
- IPFS or kubo - P2P Hypermedia Protocol
- IPFS Tools - Resources, 2 / Extension / Desktop / IPFS Cluster
▷ P2P Transfer
- ⭐ Blaze / GitHub
- ⭐ PairDrop / GitHub
- ⭐ JustBeamIt
- ⭐ SpaceDrop
- Surge - P2P App
- Wormhole
- ToffeeShare
- new.space
- FilePizza
- TransferNow
- Horizon Send
- Salad Room
- drop.lol / GitHub
- sendfilesencrypted.com
- LIGHTNING SHARE
- rDrop
- WebDrop
- MyAirBridge.com
- Sprend
- WebWormhole
- EchoDuck
- FileLove
► File Hosts
- Note - Keep in mind that it's never a good idea to upload personal or confidential files to any file host, even if they claim to be encrypted. Most file hosts only remove files after inactivity, while some delete them regardless. Check each host if you're concerned about file expiry. Tags are: Storage Size / File Size / Expiry.
- ↪️ Video File Hosts
- ⭐ Gofile - 100GB Monthly / Unlimited / 10 Days After Last Download / Cold Storage Bypass
- ⭐ Pixeldrain - Unlimited / 20GB per File / 120 Days After Last Pageview / Discord / Speedtest / Limit Bypass / Bypass Script
- ⭐ Files.vc - Unlimited / 10GB / Forever / Discord
- ⭐ Buzzheavier, 2, 3, 4 - Unlimited / 8 Days, Can Extend Forever / File Expiry / Use Adblocker / Discord
- ⭐ Catbox - Unlimited / 200MB / Forever
- ⭐ Pillowcase - Audio File Host / 200MB (500MB w/ Account) / Forever
- HIDAN - Unlimited / 10+ Days (from upload)
- Send.now - 100GB / 100GB per File / 30 Days After Last Download
- DesiUpload - Unlimited / 15 Days (15GB / 30 Days w/ Account)
- MixDrop - Unlimited / 60 Days / Account Required
- Qiwi - Account Required
- Fastupload.io - Unlimited / 30 Days (60 Days w/ Account)
- 1fichier.com - 300GB / 15 Days (30 Days w/ Account)
- Filebin - Unlimited / 6 Days / Warning
- file.kiwi - Unlimited / File Expiry Explanation
- Easyupload.io - 100GB / 30 Days
- FEX.NET - 100GB / 7 Days
- VikingFile - 500GB / 20 Days After Last Download
- DropMeFiles - 50GB / 14 Days
- GigaFile - 300GB / 100 Days
- UploadNow - 100GB / 7 Days, Can Extend Forever
- eDisk - 20GB / 30 Days
- Drop Download - 25GB / 90 Days / Account Required
- SwissTransfer - 50GB / 30 Days / 250 Downloads
- BowFile - 20GB / 20 Days
- Hexupload or AnonTransfer - 15GB / 30 Days
- Tempcloud - 10GB / 3 Days
- GrosFichiers or DataTransfer - 10GB / 14 Days
- Fshare - 10GB / 5 Days
- ShareFile, 2 - 5GB / Unlimited
- FileTransfer.io - 6GB / 21 Days / 50 Downloads
- udrop - 5GB / Forever
- Uploadev - 10GB / 180 Days After Last Download w/ Account
- Imagenetz - 5GB / 30 Days After Last Download
- FilePort - 5GB / 7 Days
- FileDitch or SendGB - 5GB / 90 Days
- MegaUp - 5GB / 60 Days
- Bestfile - 5GB / 80 Days After Last Download
- ufile.io - 5GB / 30 Days
- Internxt Send - 5GB / 15 Days
- UserDrive - 5GB / 65 Days
- pCloud Transfer or Tresorit Send - 5GB / 7 Days / Email Required
- Temp.sh - 4GB / 3 Days
- File Convoy - 3GB / 21 Days
- Send - 2.5GB / 3 Days / 10 Downloads / CLI / Instances
- JUMBOmail - 2GB / 7 Days / Email Required
- KrakenFiles - 1GB / 3 Months on Sign-Up
- DropMB - 512MB / 5 Years
- FireLoad - 2GB / 60 Days / Account Required
- FileGo - 2GB / 30 Days / Account Required
- Lufi - 2GB / 30 Days
- FilesPayouts - 10GB / Forever / Account Required
- DooDrive - 2GB / 30 Days / Account Required
- Clicknupload, 2 - 10GB / 8 Days / Account Required
- WeTransfer - 2GB / 3 Days
- Smash - 2GB / 7 Days / Email Required
- MultiUp.io / Extract / Upload or Mirrored.to - Multi Host Uploaders
- Z-o-o-m - Multi-Host Upload Desktop App
- Limited Upload Hosts - More Hosts / 1GB or Below
▷ Cloud Storage
- Note - Monthly prices are based on annual plans. 2TB prices are halved for comparison if a 1TB plan doesn't exist for a service.
- 🌐 Eylenburg Comparisons or ComparisonTabl.es - Compare Cloud Storage Sites
- ⭐ Google Drive - 15GB Free / 2 Years / ~$3 for 1TB
- ⭐ mega - 20GB Free / 3 Months / ~$4.50 for 1TB / GitHub
- disk.yandex - 5GB Free / 2 Years / $2 for 1TB
- filen - 10GB Free / 3 Months / ~$8 for 1TB / Account Required for Sharing
- terabox - 1TB Free / $3.50 for 2TB
- Dropbox - 1 or 2GB Free / 12 Months / ~$5 for 1TB / Client
- mediafire - 10GB Free / 8 Months / $5 for 1TB
- icedrive - 10GB Free / 3 Months / $5 for 1TB
- PCloud - 10GB Free / 1 Year / ~$4 for 1TB
- FebBox - 1TB Free / 1 Month / ~$4 for 2TB
- Proton Drive - 2GB Free (or 5GB for tasks) / 1 Year / ~$10 for 1TB
- JumpShare - 2GB Free / 1 Year / $8.25 for 1TB
- FileLu - 10GB / Forever / Expiry Warning
- CyberFile - 10GB Free
- MrOwl - 10GB Free / ~$16 for 1TB
- Blomp - 20GB Free / 1 Month / ~$3 for 2TB
- Akira Box - 20GB Free / 1 Years
- Backblaze B2 - 10GB Free / ~$6 for 1TB
- Cloudflare R2 - 10GB Free / ~$15.5 per 1TB
- 1Cloud File - 10GB Free
- OneDriveFly - OneDrive Indexes
- Fix-OneDrive-Zip - Fix OneDrive Zip Files >4GB
- SeaFile - Self-Hosted Cloud Storage
▷ Cloud Managers
- ⭐ Rclone - Cloud Storage Manager
- ⭐ Rclone Tools - Guide / Colab / Telegram / Transfer Tool
- ⭐ gclone - Cloud Storage Manager
- ⭐ Air Explorer - Cloud Storage Manager
- ⭐ RaiDrive - Cloud Storage Manager
- ⭐ Cyberduck - Libre Server / Cloud Storage Browser / GitHub
- SpaceDrive - Cloud Storage Manager
- AList - Cloud Storage Manager
- MultCloud - Cloud Storage Manager
- xpipe - Remote File Manager
▷ Google Drive Tools
- ⭐ OneClickRun - Google Drive Tools Colab / Features / Use Throwaways
- Any File to Google Drive - DDL to Google Drive Tool
- DriveUploader - Receive Files via Google Drive
- ZIP Extractor - Google Drive / Gmail File Archiver
- Google Drive CLI - Google Drive CLI Client
- goodls - Google Drive Downloader
- Google Drive Downloader - Google Drive Folder Downloader
- gdrivedl - Google Drive Python Download Script
- ISAAC - Google Service Account Generators
- goindex-extended / Themes or Google-Drive-Index - Google Drive Indexers
- gdurl, GDrive Link Generator, Direct.GDrive, Maulvi or GDriveWebAppPublic - Host Direct Links on Google Drive
- GdriveCloneWeb or Google Drive Clone Bot / GitHub - Copy Google Drives
- GD-EFC Link Encryptor - Google Drive Link Encryptor for GD-EFC
- gd-efc - Copy Encrypted Google Drive
- DriveRename - Bulk Google Drive File Rename
- Sharer, YuShare or GDToT - Google Drive File Sharing
▷ MEGA Tools
- ⭐ Megabasterd - Download Quota Bypass / Note
- ⭐ Mega Account Generators - Account Gen / Unlimited Upload Size / Fix
- MEGA Desktop / GitHub - Official GUI App
- MEGA CMD / GitHub - Official CLI App
-
 @ 119356ac:740a8b90
2025-05-14 23:03:31
@ 119356ac:740a8b90
2025-05-14 23:03:31► System Tools
- Warning - It's not recommended to use debloaters unless you know what you're doing. Always research first, never just "Apply All" randomly.
- 🌐 Awesome Windows 11 - Windows 11 Resources
- 🌐 PC-Optimization-Hub - System Optimization Resources
- ↪️ Gaming Optimization
- ⭐ PowerToys - System Tools / Search / Plugins / GitHub
- ⭐ Sysinternals - Advanced System Tools / Suite
- ⭐ CPU-Z, winfetch, CPU Fetch, Glow or GPU-Z - System Info Tools
- ⭐ SuperF4 or FKill - Process Killers
- VCRedist - AIO Repack for Microsoft Visual C++ Redists
- Windows-11-Guide or Pastas - Windows Guides
- NanaRun - System Admin Tools
- PolicyPlus - Local Group Policy Editor
- PowerPlanSwitcher - Quickly Change Power Schemes
- Scheduler or TaskRunner - System Task Scheduler
- CoreTemp or System Informer - Process Monitors
- ThrottleStop - Laptop CPU Monitor / Optimizer
- RegExp, RegScanner, ripgrep-all or Registry-Finder - Registry Explorers / Scanners
- WinbIndex - Windows System Files / Binaries
- OfflineInsiderEnroll - Enable Windows Insider without Account
- WLSetup-All - Windows Live Essentials 2012 Archive
- Rhasspy - Voice Assistant
- OpenRecall or Windrecorder - Memory Search App / System Recorders
- Time.is - Check Accuracy of System Clock
- G-Helper - Armoury Crate Replacement
- LenovoLegionToolkit - Lenovo Vantage Replacement
▷ System Debloating
- ⭐ Debloat Guide - Windows Debloat Guide
- ⭐ Bulk Crap Uninstaller, Revo Uninstaller or GeekUninstaller - Bulk Uninstallation Tools
- ⭐ SophiaScript - Debloater
- BleachBit - Clean System Storage
- GhostBuster or Device Cleanup Tool - Remove Non-Present Devices
- Win11Debloat - Debloater
- Should I Remove It? - Program Removal Guide
▷ System Tweaks
- ⭐ Windhawk, MajorGeeks Windows Tweaks, Winaero or - System Tweaking Tools / Warning
- ⭐ EverythingToolbar or yasb - Tweaked Taskbars
- ⭐ Open Shell - Tweak Start Menu / Start Skin
- ⭐ EarTrumpet, Volumey or Volume2 - Tweak Volume Mixer
- ⭐ AltSnap - Tweaked Windows Dragging
- abbodi1406, BatUtil or TechNet-Gallery - System Scripts
- Win10 Widgets or Eww - Widgets for Windows
- Wintoys - System App Tweaking
- Wox, Listary, FlowLauncher, Ueli / GitHub - Keystroke / App Launchers
- Kando - App Launcher / Pie Menu / GitHub / Discord
- Hunt and Peck or Cerebro App - Tweaked System Navigation
- SmartSystemMenu - Tweak System Menu
- EasyContextMenu, Nilesoft Shell or ContextMenuManager
- RCWM - Tweaked Context Menus
- Explorer Tab Utility - Tweaked File Explorer
- Spencer - Classic Start Menu
- Taskbar Tweaker - Taskbar Advanced Features
- Taskbar Hide - Easily Hide / Show Taskbar
- QuickLook - macOS Quick Look for Windows
- TopNotify - Move Windows Notifications
▷ Package Managers
- ⭐ WinGet - CLI Package Manager / Repos / Automation / Auto Update / GitHub
- ⭐ UniGetUI - GUI for Popular Package Managers
- ⭐ Scoop - Portable Package Manager
- ⭐ sfsu or hok - Fast Scoop Utilities
- Spinel - Multi-Program Install Script Generator
- Chocolatey / GUI / GitHub, Patch My PC or RuckZuck - Package Managers
- Silent Install - Build Multi-Program Installers
- 0Install - Decentralized Cross-Platform Package Manager
- portableapps - Package Manager for Portable Apps
- Baulk - Minimalist Package Manager
- NirLauncher - Portable Package Manager for NirSoft Utilities
▷ Task Automation
- 🌐 Awesome AutoHotkey - AutoHotkey Resources
- 🌐 Awesome AutoIt - AutoIt Resources
- ⭐ AutoHotkey / Discord
- AutoIt
- Tinytask
- Power Automate
- sikulix
- ChoEazyCopy
▷ Terminal / CLI
- 🌐 The Terminal Directory - List of Terminal Emulators
- 🌐 terminals-are-sexy - Terminal Resources
- 🌐 Awesome CLI Apps or Command Line Tools - Command Line Resources
- ⭐ ss64 - Command Line Reference Index
- Windows Terminal / 2, ConEmu, Hyper, Tabby, MobaXterm or WezTerm - Windows Terminal Emulators
- BusyBox - Unix Commands for Windows
- Clink - Command Line Editing
- Nushell - Alt Shell
- Tiny Care Terminal - Terminal Dashboard That Cares
- Command Challenge - Command Line Learning
- Mintty - Cygwin Terminal Emulator
- GetDNote - Command Line Notebook
- PowerShell - Windows / macOS / Linux PowerShell
- LeanandMean - Powershell Snippets / Use with Caution
- PowerShell Scripts or WindowsPowerShell - Alt Shell Scripts
- Starship - Cross-Shell Prompt
▷ Remote Desktop
- ⭐ Parsec - Desktop Client / X / Discord
- ⭐ RustDesk - Desktop Client / Subreddit / Discord / GitHub
- ⭐ Aspia - Desktop Client / Telegram / GitHub
- ⭐ Sunshine - Gaming Remote Desktop Client / Discord / GitHub
- Moonlight - Gaming Remote Desktop Client / Discord / GitHub
- Arcane - Desktop Client
- HopToDesk - Desktop Client / GitLab
- CoScreen - Desktop Client
- Remotly - Desktop Client
- Bananas - Desktop Client / Discord / GitHub
- ChromeRemoteDesktop - Web-Based
- InputDirector - Multi-Computer Client
- Mouse Without Borders - Multi-Computer Client
- p2p - Portable Client
- Screensy - Web-Based / GitHub
- Screego - Web-Based / GitHub
- Screen-Sharing - Web-Based / GitHub
- TigerVNC - VNC Client / GitHub
- TightVNC - VNC Client
- noVNC - JavaScript VNC Client / GitHub
▷ Clipboard Managers
- ⭐ Ditto - Clipboard Manager / GitHub
- PasteBar - Clipboard Manager / GitHub
- CrossPaste - Clipboard Manager / GitHub
- ArsClip - Clipboard Manager
- ClipAngel - Clipboard Manager
- CopyQ / GitHub or XClipper / GitHub - Clipboard Managers with Editing and Scripting Features
- MultiClipBoardSlots - Extend Clipboard by 10 Memory Slots
▷ Window Managers
- ⭐ GlazeWM - Tiling Window Manager Inspired by i3wm
- ⭐ Komorebi or WorkSpacer / GitHub - Tiling Window Managers
- Whim - Pluggable Dynamic Window Manager
- DWM - Port of X11 dwm to Windows
▷ Virtual Machines
- 🌐 Awesome Web Desktops or Simone's Computer - OS Emulators / VMs
- ↪️ Android Emulators
- ↪️ Hackintosh Resources
- ⭐ VMware Workstation or VirtualBox / Portable - Virtual Machines
- ⭐ Virt-Manager / GitHub, MultiPass / GitHub or Vagrantup / GitHub - Virtual Machine Managers
- Looking Glass - App for Using Kernel-Based Virtual Machine Configured for VGA PCI Pass-Through / GitHub
- Qemu, Hyper-V or Denodo Test - Virtual Machines
- OSBoxes - Preinstalled Virtual Machine
- Terminator - Online Virtual Machines
- JSLinux - Online Linux Virtual Machines
- QuickEmu or Dexpot - Virtual Machine Creator
- Virtual x86 - x86-compatible OS Emulators
- PCjs Machines - Classic Computer Emulators
- InfiniteMac - Apple OS Emulators
- winevdm - 16-bit Windows on 64-bit Systems
- Blink - Linux Emulator for Windows
- Dockerholics - Docker Apps
- WebCatalog - Turn Sites into Desktop Apps
► Hardware Tools
- ↪️ PC Building / Shopping
- ⭐ PSU Calculator - Find Compatible Power Supplies
- DeviceTests - Multiple Device Tests
- NotCPUCores, BES, ParkControl, QuickCPU or Process Lasso - CPU Optimizer
- Ozone3D, UNIGINE Benchmarks or OCCT - System Benchmarking
- Testmem5 - Memory Benchmarking
- MemTest - Memory Diagnostic Tool
- SDIO, Drivers Collection, Driverscape or DriverStoreExplorer - Update / Install Missing Drivers / Note
- VOGONS - Vintage Computer Hardware Forum
▷ Hardware Monitors
- ⭐ HWiNFO - System Info & Monitoring
- Scrutiny, GSmartControl / GitHub or smartmontools - Hard Drive Monitors
- CoolerControl - Cooling Device Monitor
- BatteryMode - System Tray Battery Percentage / Managers / GitHub
- HWMonitor - Hardware Monitors
- fastfetch - System Info & Monitoring
- Task Manager DeLuxe - Task Manager Alt
- Libre Hardware Monitor - Updated Fork of Open Hardware Monitor
- FanControl / GitHub or FanCtrl - PC Fan Controllers
- Traffic Monitor - Network & Hardware Monitor
- bottom or Glances / GitHub - Terminal Hardware Monitors
▷ GPU Tools
- ⭐ NVTOP - GPU / Accelerator Process Monitor
- ⭐ GreenWithEnvy - Manage / Control NVIDIA Cards
- ⭐ NVCleanstall or NVSlimmer - NVIDIA Driver Packages
- Display Driver Uninstaller, 2 - Display Driver Removal Tool / GitHub
- TinyNvidiaUpdateChecker - NVIDIA GPU Update Checker
- nvidiaProfileInspector - Modify / View Hidden NVIDIA Settings / Guide
- RadeonSoftwareSlimmer - Debloat AMD Drivers
- R.ID - AMD 3rd Party Drivers / Discord
- SMCAMDProcessor - AMD Processor Power Management
- PresentMon - GPU Benchmarking
- Universal x86 Tuning Utility - Laptop GPU Controller / GitHub
- RyzenAdj - Ryzen Laptop GPU Controller
▷ Disk Tools
- 🌐 Awesome Storage - File Storage Resources
- 🌐 Awesome DataHoarding - Data Hoarding Resources
- ⭐ WizTree - Disk Usage Analyzer
- ⭐ CrystalDiskMark or CCISOBench - Disk Benchmarking Tools
- ⭐ GParted / GitLab, MiniTool Partition Wizard or AOMEI Partition Assistant / Unlocker - Partition Managers
- ⭐ Validrive - Check True Storage Size of USB Devices
- WinDirStat - Disk Usage Analyzer / Cleanup Tool / GitHub
- TrueNAS - Storage System
- QDirStat - Directory Statistics
- CrystalDiskInfo - S.M.A.R.T. Data Analyzer
- Macrorit Partition Expert or Diskovery - Disk Usage Analyzers
- Gdu or dua - Disk Usage Analyzer with Parallel Processing
- Erdtree - Cross-Platform Disk Usage Analyzer
- PC Manager - Disk Managers / Cleanup
- Air Live Drive - Mount Cloud Drives as Local Disks
- SFTPDrive - Mount SFTP Servers as Local Disks
▷ Monitor Tools
- ⭐ DisplayFusion or Dual Monitor Tool - Dual Monitor Tools
- ⭐ f.lux, LightBulb, ScreenTemperature or SunsetScreen - Adjust Display Color / Temperature
- ⭐ Monitorian, Twinkle Tray / GitHub or Dimmer - Adjust Monitor Brightness
- EIZO, Monitor or LCDTech - Monitor Performance Tests
- TestUFO - Monitor Framerate Test
- LittleBigMouse - DPI Test
- Scalizer - Auto DPI Scaling / YouTube
- ICM or ICC Profiles - ICC Profiles and Monitor Calibration
- Display Calc - Display Distance / Dimension Calculator
- Multi-Monitor Calculator - Dual-Monitor Setup Planning / Tests
- Wide Gamut - Color Compatibility Test
- Dead.Pixel - Dead Pixel Test
- JScreenFix - Repair Stuck Pixels
- CenterOfMyScreen - Find Center of Monitor
- ShowDesktopOneMonitor - Show Desktop for Only One Monitor
- Deskreen / GitHub or SpaceDesk - Use Mobile Device as Monitor
- ShaderGlass - Custom Screen Shaders
- DaltonLens or Toptal - Color Blindness Filters
- NVDA - Screen Reader for Blind Users / GitHub
▷ Mouse / Keyboard
- ⭐ /r/MechanicalKeyboards Wiki - Mechanical Keyboard Resources
- ⭐ Hotkey Cheatsheet, Use The Keyboard, HotkeyP, Clavier++, Kinto or CheatKeys - Keyboard Shortcuts / Image, 2 / Course
- ⭐ VIA / GitHub, SharpKeys, Kanata, keymapper, Ergogen, Mahou - Custom Keyboard Layouts / Remapping
- ⭐ geekhack or KeebTalk - Keyboard Forums
- X-Mouse Button Control - Re-Map Mouse Buttons / Scroll Wheel
- MoveMouse or MouseJiggler - Simulate User Activity
- Raw Accel - Mouse Acceleration Tool
- StrokeIt - Mouse Gestures
- Espanso - Typing Shortcuts / GitHub
- win-vind - Vim Style Keybindings for Windows
- Vial - Custom Keyboard Config Tool
- KeyViz - Keystroke Visualizer
- WhatPulse - Mouse / Keyboard Usage Analyzer
- Kmonad - Keyboard Manager
- Deskhop - Quickly Switch Devices between Computers
- Switchy - Switch Keyboard Languages with Button
- Is this good? - Custom Keyboard Guides
- DreyMaR's - Keyboard Tips and Resources
- Keyboard University or KDB - Mechanical Keyboard Building Guides
- Cosmos - Create Custom Keyboards
- Keyboard Simulator - Design & Test Virtual Keyboards
- Key Test - Keyboard Tester
▷ System Audio
- ⭐ Equalizer APO, 2 / GUI, AutoEq, Dolby Access / Note or FXSound - Audio Equalizers
- Wave Link or VoiceMeeter / Banana - Audio Mixers / Multi-Device Playback
- SoundSwitch - Switch Audio Device with Hotkey / GitHub
- SonyHeadphonesClient - Sony Headphones Clone
- Audiocheck - Audio Tests
- LowAudioLatency - Reduce Audio Latency
- DigitalFeed - Lossless Audio Sound System Test
- Online Mic Test or Check Mic - Mic Test
- Sound Meter or REW - Measure Surrounding Sound Level
- Krisp or noise-suppression-for-voice - Noise Suppression Tools
- AirPods Dirty Secret - AirPods Repair Directory
► Windows ISOs
- ⭐ Genuine Installation Media - Windows ISOs / Clean Install Guide
- files.rg-adguard or MVS dump - Verify ISO Legitimacy
- OS.click, MyDigitalLife or Microsoft SD - Windows ISOs
- Old School OS, OS Vault, VETUSWARE or WinWorldPC - Oldschool ISOs
- Fido - ISO Powershell Script
- NetBoot - Boot Operating Systems without ISOs
- CoolStar - Install Windows on Chromebook
▷ USB / Bootloaders
- ⭐ Rufus - Create Bootable USB Drives
- ⭐ YUMI - Create Bootable USB Drives
- MediaCreationTool - Windows Deployment Automation
- USBTreeView - USB Device Tree Viewer
- CloverBootloader or EasyBCD - Bootloaders / Config
▷ Windows Activation
- ⭐ MAS - Activation Scripts / Windows / Office / Discord
- ⭐ KMS_VL_ALL_AIO - Offline Activator / Windows / Office
- OfficeRTool - Offline Activator / Office
▷ Windows Updates
- ⭐ Windows 10 After EOL - Receive Windows Updates After Win10's End-Of-Life
- ⭐ ChangeWindows - Latest Windows Update Info
- stopupdates10 or InControl - Enable / Disable Win 10/11 Updates / Can Cause Breakage
- LegacyUpdate - Fix Windows Updates for Legacy Editions
- Extended Win 7 Updates - Extended Windows 7 Updates
- WURefresh - Reset Windows Update Components
- UUP Dump or Microsoft Update Catalog - Download Previous Windows Updates
- PC Health Check or WhyNotWin11 - Identify why your PC isn't Ready for Windows 11
- FlashMyBoard - Receive Motherboard Update Notifications
▷ Windows Repair
- MagNumDB, ErrorLookup or Microsoft Error Lookup - Windows Debugging Tools
- /r/TechSupport / Wiki - Tech Support Subreddit / Discord
- Hardforum, TechGuy, Eleven Forums or Ten Forums - Tech Support Forums
- Medicat - Computer Diagnostic / Recovery Toolkit / GitHub
- PhoenixPE - Recovery Environment
- Hiren's BootCD PE or Win10XPE - Preinstallation Environments / Recovery
- Magic Trace - Diagnose Performance Issues using Intel Processor Trace
► Customization
- 🌐 Windows-Ricing or Heliohost Guide - Windows Ricing Resources
- ⭐ Rainmeter - Desktop Customization / Discord
- ⭐ OpenRGB / Beta, WLED, Aurora, LiquidCTL, Artemis, RGBSync, SignalRGB or FireLight - RGB Lighting Control
- ⭐ VSThemes, WindowsCustomization or 7Themes - Theme Indexes
- Styled Themes - Anime / Modern Style / macOS Style, 2 / Old School Style, 2
- VirtualCustoms or winthemers - Customization Communities
- Desktops - Customization Showcases
- XDesktopSoft - Desktop Customization
- SecureUxTheme or UltraUXThemePatcher - UX Patcher
- Cursormania Archive - Cursors
- MacOS Cursors for Windows, CursorOS or macOS-cursors-for-Windows - macOS Style Cursors
- Mechvibes / GitHub or MechaKeys - Keyboard Sound Effects
- ElectricSheep or After Dark CSS - Screensavers
- FolderMarker, Flaired Folder, CustomFolder - Custom Folder Icons
- Recycle Bin Themes - Custom Recycle Bin Icons
- msstyleEditor - Visual Style Editor
- StartIsBack or StartAllBack - Start Menu Customization
- Taskbar Tweaker, TranslucentTB, NiceTaskbar - Taskbar Customization / Old School Style
- AccentColorizer - Accent Color Customization
- BeautySearch - Search Customization
- ElevenClock - Clock Customization
- HackBGRT - Boot Logo Changer
- WinDynamicDesktop or Dynamic Theme - Auto Change Wallpaper
- ExplorerBlurMica - File Explorer Effects
- MicaForEveryone - Title Bar Effects
- Cute Borders - Border Color Changer (Win11 Only)
- ModernFlyouts - Modern Flyouts / GitHub
- Alternative Windows Shells Wiki - Alt Windows Shells
- Aerial - Apple TV Screensaver
- ExcelDarkThemeFix - Fix Excel on Themed Windows
- MacType - Use Mac Fonts on Windows / GitHub
▷ App Themes
- ⭐ Dracula / Discord or Catppuccin / Discord - Custom App Themes
- ⭐ terminal.sexy, TerminalSplash, Solarized or WindowsTerminalThemes - Terminal Themes
- Rosé Pine / Discord, Aura Theme or theme.park - Custom App Themes
- Totally Awesome List - Old School App Themes
- Pokemon Terminal - Pokémon Terminal Themes
- Traffic Monitor - System Monitor Themes
▷ Wallpapers
- ⭐ wallhaven.cc - Search Wallpapers / Downloader / Client
- ⭐ Wallpaper Abyss, WallpaperCave, WallpapersCraft, VSThemes - Search Wallpapers
- ⭐ Rev Wallpaper or r/WallpaperRequests - Reverse Wallpaper Search
- ⭐ Studio Ghibli Wallpapers or Ghibli Upscaled - Studio Ghibli Wallpapers
- ⭐ Ultimate Windows Wallpack / Wiki, Spotlight - Windows Wallpapers
- ⭐ LWP, /r/LivingBackgrounds, WALLegend or MoeWalls - Live Wallpapers
- /r/Wallpaper - Wallpapers Community
- DualMonitorBackgrounds - Dual Monitor Wallpapers
- Scenic Illustrations - Landscape Wallpapers
- CoolBackgrounds - Customizable Wallpapers
- Simple Desktops, Minimalistic Wallpaper, Positron Dream or SetAsWall - Minimalist Wallpapers
- Aesthetic Wallpapers - Aesthetic Wallpapers
- Mac Walls or BasicAppleBlog - Apple Wallpapers
- ChromecastBG - Chromecast Wallpapers
- Bing Wallpaper Archive - Bing Wallpapers
- Xbox Wallpapers - Xbox Wallpapers
- Screencaps or shot.cafe - Movie / TV Wallpapers
- Anime Pictures, WallpaperWaifu, TheOtaku or MyLiveWallpapers - Anime Wallpapers
- WallsPic, WallpaperFlare, HDQwalls or UHD Wallpaper - Misc Wallpapers
- G_Walls - Telegram Wallpaper Channels
▷ Wallpaper Tools
- ⭐ Wallpaper Engine / PKG to Zip / Collections, 2 / Workshop DL - Wallpaper Manager
- ⭐ Lively or ScreenPlay - Live Wallpaper Manager
- backiee - Wallpaper Manager
- SuperPaper - Cross-Platform Multi-Monitor Wallpaper Manager
- Background Switcher - Multi-Host Wallpaper Switcher
- Faerber - Edit Wallpapers to Match Color Scheme
- AutoWall - Turn Videos / GIFs to Live Wallpapers
- Awesome Wallpaper - Show System Information on Wallpaper