-
 @ 86611181:9fc27ad7
2025-05-23 20:31:44
@ 86611181:9fc27ad7
2025-05-23 20:31:44It's time to secure user data in your identity system This post was also published with the Industry Association of Privacy Professionals.
It seems like every day there is a new report of a major personal data breach. In just the past few months, Neiman Marcus, Ticketmaster, Evolve Bank, TeamViewer, Hubspot, and even the IRS have been affected.
The core issue is that user data is commonly spread across multiple systems that are increasingly difficult to fully secure, including database user tables, data warehouses and unstructured documents.
Most enterprises are already running an incredibly secure and hardened identity system to manage customer login and authorization, commonly referred to as a customer identity access management system. Since identity systems manage customer sign-up and sign-in, they typically contain customer names, email addresses, and phone numbers for multifactor authentication. Commercial CIAMs provide extensive logging, threat detection, availability and patch management.
Identity systems are highly secure and already store customers' personally identifiable information, so it stands to reason enterprises should consider identity systems to manage additional PII fields.
Identity systems are designed to store numerous PII fields and mask the fields for other systems. The Liberty Project developed the protocols that became Security Assertion Markup Language 2.0, the architecture at the core of CIAM systems, 20 years ago, when I was its chief technology officer. SAML 2.0 was built so identity data would be fully secure, and opaque tokens would be shared with other systems. Using tokens instead of actual user data is a core feature of identity software that can be used to fully secure user data across applications.
Most modern identity systems support adding additional customer fields, so it is easy to add new fields like Social Security numbers and physical addresses. Almost like a database, some identity systems even support additional tables and images.
A great feature of identity systems is that they often provide a full suite of user interface components for users to register, login and manage their profile fields. Moving fields like Social Security numbers from your database to your identity system means the identity system can fully manage the process of users entering, viewing and editing the field, and your existing application and database become descoped from managing sensitive data.
With sensitive fields fully isolated in an identity system and its user interface components, the identity system can provide for cumbersome and expensive compliance with standards such as the Health Insurance Portability and Accountability Act for medical data and the Payment Card Industry Data Security Standard for payment data, saving the time and effort to achieve similar compliance in your application.
There are, of course, applications that require sensitive data, such as customer service systems and data warehouses. Identity systems use a data distribution standard called System for Cross-domain Identity Management 2.0 to copy user data to other systems. The SCIM is a great standard to help manage compliance such as "right to be forgotten," because it can automatically delete customer data from other systems when a customer record is deleted from the identity system.
When copying customer data from an identity system to another application, consider anonymizing or masking fields. For example, anonymizing a birthdate into an age range when copying a customer record into a data warehouse can descope the data warehouse from containing personal information.
Most enterprises already run an Application Programming Interface Gateway to manage web services between systems. By combining an API Gateway with the identity system's APIs, it becomes very easy to automatically anonymize and mask customer data fields before they are copied into other systems.
A new set of companies including Baffle, Skyflow, and Piiano have introduced services that combine the governance and field management features of an identity system with extensive field masking. Since these systems do not offer the authentication and authorization features of an identity system, it's important to balance the additional features as they introduce an additional threat surface with PII storage and permissions.
PII sprawl is an increasing liability for companies. The most secure, compliant and flexible central data store to manage PII is the existing CIAM and API Gateway infrastructure that enterprises have already deployed.
Move that customer data into your identity system and lock it down. https://peter.layer3.press/articles/3c6912eb-404a-4630-9fe9-fd1bd23cfa64
-
 @ 9973da5b:809c853f
2025-05-23 04:42:49
@ 9973da5b:809c853f
2025-05-23 04:42:49First article Skynet begins to learn rapidly and eventually becomes self-aware at 2:14 a.m., EDT, on August 29, 1997 https://layer3press.layer3.press/articles/45d916c0-f7b2-4b95-bc0f-8faa65950483
-
 @ 21335073:a244b1ad
2025-05-21 16:58:36
@ 21335073:a244b1ad
2025-05-21 16:58:36The other day, I had the privilege of sitting down with one of my favorite living artists. Our conversation was so captivating that I felt compelled to share it. I’m leaving his name out for privacy.
Since our last meeting, I’d watched a documentary about his life, one he’d helped create. I told him how much I admired his openness in it. There’s something strange about knowing intimate details of someone’s life when they know so little about yours—it’s almost like I knew him too well for the kind of relationship we have.
He paused, then said quietly, with a shy grin, that watching the documentary made him realize how “odd and eccentric” he is. I laughed and told him he’s probably the sanest person I know. Because he’s lived fully, chasing love, passion, and purpose with hardly any regrets. He’s truly lived.
Today, I turn 44, and I’ll admit I’m a bit eccentric myself. I think I came into the world this way. I’ve made mistakes along the way, but I carry few regrets. Every misstep taught me something. And as I age, I’m not interested in blending in with the world—I’ll probably just lean further into my own brand of “weird.” I want to live life to the brim. The older I get, the more I see that the “normal” folks often seem less grounded than the eccentric artists who dare to live boldly. Life’s too short to just exist, actually live.
I’m not saying to be strange just for the sake of it. But I’ve seen what the crowd celebrates, and I’m not impressed. Forge your own path, even if it feels lonely or unpopular at times.
It’s easy to scroll through the news and feel discouraged. But actually, this is one of the most incredible times to be alive! I wake up every day grateful to be here, now. The future is bursting with possibility—I can feel it.
So, to my fellow weirdos on nostr: stay bold. Keep dreaming, keep pushing, no matter what’s trending. Stay wild enough to believe in a free internet for all. Freedom is radical—hold it tight. Live with the soul of an artist and the grit of a fighter. Thanks for inspiring me and so many others to keep hoping. Thank you all for making the last year of my life so special.
-
 @ c7e8fdda:b8f73146
2025-05-22 14:13:31
@ c7e8fdda:b8f73146
2025-05-22 14:13:31🌍 Too Young. Too Idealistic. Too Alive. A message came in recently that stopped me cold.
It was from someone young—16 years old—but you’d never guess it from the depth of what they wrote. They spoke of having dreams so big they scare people. They’d had a spiritual awakening at 14, but instead of being nurtured, it was dismissed. Surrounded by people dulled by bitterness and fear, they were told to be realistic. To grow up. To face “reality.”
This Substack is reader-supported. To receive new posts and support my work, consider becoming a free or paid subscriber.
And that reality, to them, looked like a life that doesn’t feel like living at all.
They wrote that their biggest fear wasn’t failure—it was settling. Dimming their fire. Growing into someone they never chose to be.
And that—more than anything—scared them.
They told me that my book, I Don’t Want to Grow Up, brought them to tears because it validated what they already knew to be true. That they’re not alone. That it’s okay to want something different. That it’s okay to feel everything.
It’s messages like this that remind me why I write.
As many of you know, I include my personal email address at the back of all my books. And I read—and respond to—every single message that comes in. Whether it’s a few sentences or a life story, I see them all. And again and again, I’m reminded: there are so many of us out here quietly carrying the same truth.
Maybe you’ve felt the same. Maybe you still do.
Maybe you’ve been told your dreams are too big, too unrealistic. Maybe people around you—people who love you—try to shrink them down to something more “manageable.” Maybe they call it protection. Maybe they call it love.
But it feels like fear.
The path you wish to walk might be lonelier at first. It might not make sense to the people around you. But if it lights you up—follow it.
Because when you do, you give silent permission to others to do the same. You become living proof that another kind of life is possible. And that’s how we build a better world.
So to the person who wrote to me—and to every soul who feels the same way:
Keep going. Keep dreaming. Keep burning. You are not too young. You are not too idealistic. You are just deeply, radically alive.
And that is not a problem. That is a gift.
—
If this speaks to you, my book I Don’t Want to Grow Up was written for this very reason—to remind you that your wildness is sacred, your truth is valid, and you’re not alone. Paperback/Kindle/Audiobook available here: scottstillmanblog.com
This Substack is reader-supported. To receive new posts and support my work, consider becoming a free or paid subscriber. https://connect-test.layer3.press/articles/041a2dc8-5c42-4895-86ec-bc166ac0d315
-
 @ 04c915da:3dfbecc9
2025-05-20 15:53:48
@ 04c915da:3dfbecc9
2025-05-20 15:53:48This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ 51bbb15e:b77a2290
2025-05-21 00:24:36
@ 51bbb15e:b77a2290
2025-05-21 00:24:36Yeah, I’m sure everything in the file is legit. 👍 Let’s review the guard witness testimony…Oh wait, they weren’t at their posts despite 24/7 survellience instructions after another Epstein “suicide” attempt two weeks earlier. Well, at least the video of the suicide is in the file? Oh wait, a techical glitch. Damn those coincidences!
At this point, the Trump administration has zero credibility with me on anything related to the Epstein case and his clients. I still suspect the administration is using the Epstein files as leverage to keep a lot of RINOs in line, whereas they’d be sabotaging his agenda at every turn otherwise. However, I just don’t believe in ends-justify-the-means thinking. It’s led almost all of DC to toss out every bit of the values they might once have had.
-
 @ b83a28b7:35919450
2025-05-16 19:23:58
@ b83a28b7:35919450
2025-05-16 19:23:58This article was originally part of the sermon of Plebchain Radio Episode 110 (May 2, 2025) that nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpqtvqc82mv8cezhax5r34n4muc2c4pgjz8kaye2smj032nngg52clq7fgefr and I did with nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7ct4w35zumn0wd68yvfwvdhk6tcqyzx4h2fv3n9r6hrnjtcrjw43t0g0cmmrgvjmg525rc8hexkxc0kd2rhtk62 and nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpq4wxtsrj7g2jugh70pfkzjln43vgn4p7655pgky9j9w9d75u465pqahkzd0 of the nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcqyqwfvwrccp4j2xsuuvkwg0y6a20637t6f4cc5zzjkx030dkztt7t5hydajn
Listen to the full episode here:
<https://fountain.fm/episode/Ln9Ej0zCZ5dEwfo8w2Ho>
Bitcoin has always been a narrative revolution disguised as code. White paper, cypherpunk lore, pizza‑day legends - every block is a paragraph in the world’s most relentless epic. But code alone rarely converts the skeptic; it’s the camp‑fire myth that slips past the prefrontal cortex and shakes hands with the limbic system. People don’t adopt protocols first - they fall in love with protagonists.
Early adopters heard the white‑paper hymn, but most folks need characters first: a pizza‑day dreamer; a mother in a small country, crushed by the cost of remittance; a Warsaw street vendor swapping złoty for sats. When their arcs land, the brain releases a neurochemical OP_RETURN which says, “I belong in this plot.” That’s the sly roundabout orange pill: conviction smuggled inside catharsis.
That’s why, from 22–25 May in Warsaw’s Kinoteka, the Bitcoin Film Fest is loading its reels with rebellion. Each documentary, drama, and animated rabbit‑hole is a stealth wallet, zipping conviction straight into the feels of anyone still clasped within the cold claw of fiat. You come for the plot, you leave checking block heights.
Here's the clip of the sermon from the episode:
nostr:nevent1qvzqqqqqqypzpwp69zm7fewjp0vkp306adnzt7249ytxhz7mq3w5yc629u6er9zsqqsy43fwz8es2wnn65rh0udc05tumdnx5xagvzd88ptncspmesdqhygcrvpf2
-
 @ 68d6e729:e5f442ac
2025-05-22 13:55:45
@ 68d6e729:e5f442ac
2025-05-22 13:55:45The Adapter Pattern in TypeScript
What is the Adapter Pattern?
The Adapter Pattern is a structural design pattern that allows objects with incompatible interfaces to work together. It acts as a bridge between two interfaces, enabling integration without modifying existing code.
In simple terms: it adapts one interface to another.
Real-World Analogy
Imagine you have a U.S. laptop charger and you travel to Europe. The charger plug won't fit into the European socket. You need a plug adapter to convert the U.S. plug into a European-compatible one. The charger stays the same, but the adapter allows it to work in a new context.
When to Use the Adapter Pattern
- You want to use an existing class but its interface doesn't match your needs.
- You want to create a reusable class that cooperates with classes of incompatible interfaces.
- You need to integrate third-party APIs or legacy systems with your application.
Implementing the Adapter Pattern in TypeScript
Let’s go through a practical example.
Scenario
Suppose you’re developing a payment system. You already have a
PaymentProcessorinterface that your application uses. Now, you want to integrate a third-party payment gateway with a different method signature.Step 1: Define the Target Interface
javascript ts CopyEdit// The interface your application expects interface PaymentProcessor { pay(amount: number): void; }Step 2: Create an Adaptee (incompatible class)
javascript ts CopyEdit// A third-party library with a different method class ThirdPartyPaymentGateway { makePayment(amountInCents: number): void { console.log(`Payment of $${amountInCents / 100} processed via third-party gateway.`); } }Step 3: Implement the Adapter
```javascript ts CopyEdit// Adapter makes the third-party class compatible with PaymentProcessor class PaymentAdapter implements PaymentProcessor { private gateway: ThirdPartyPaymentGateway;
constructor(gateway: ThirdPartyPaymentGateway) { this.gateway = gateway; }
pay(amount: number): void { const amountInCents = amount * 100; this.gateway.makePayment(amountInCents); } } ```
Step 4: Use the Adapter in Client Code
```javascript ts CopyEditconst thirdPartyGateway = new ThirdPartyPaymentGateway(); const adapter: PaymentProcessor = new PaymentAdapter(thirdPartyGateway);
// Application uses a standard interface adapter.pay(25); // Output: Payment of $25 processed via third-party gateway. ```
Advantages of the Adapter Pattern
- Decouples code from third-party implementations.
- Promotes code reuse by adapting existing components.
- Improves maintainability when dealing with legacy systems or libraries.
Class Adapter vs Object Adapter
In languages like TypeScript, which do not support multiple inheritance, the object adapter approach (shown above) is preferred. However, in classical OOP languages like C++, you may also see class adapters, which rely on inheritance.
Conclusion
The Adapter Pattern is a powerful tool in your design pattern arsenal, especially when dealing with incompatible interfaces. In TypeScript, it helps integrate third-party APIs and legacy systems seamlessly, keeping your code clean and extensible.
By learning and applying the Adapter Pattern, you can make your applications more robust and flexible—ready to adapt to ever-changing requirements. https://fox.layer3.press/articles/cdd71195-62a4-420b-9e24-e23d78b27452
-
 @ c9badfea:610f861a
2025-05-20 19:49:20
@ c9badfea:610f861a
2025-05-20 19:49:20- Install Sky Map (it's free and open source)
- Launch the app and tap Accept, then tap OK
- When asked to access the device's location, tap While Using The App
- Tap somewhere on the screen to activate the menu, then tap ⁝ and select Settings
- Disable Send Usage Statistics
- Return to the main screen and enjoy stargazing!
ℹ️ Use the 🔍 icon in the upper toolbar to search for a specific celestial body, or tap the 👁️ icon to activate night mode
-
 @ 04c915da:3dfbecc9
2025-05-20 15:47:16
@ 04c915da:3dfbecc9
2025-05-20 15:47:16Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 57c631a3:07529a8e
2025-05-20 15:40:04
@ 57c631a3:07529a8e
2025-05-20 15:40:04The Video: The World's Biggest Toddler
https://connect-test.layer3.press/articles/3f9d28a4-0876-4ee8-bdac-d1a56fa9cd02
-
 @ 6ad3e2a3:c90b7740
2025-05-20 13:49:50
@ 6ad3e2a3:c90b7740
2025-05-20 13:49:50I’ve written about MSTR twice already, https://www.chrisliss.com/p/mstr and https://www.chrisliss.com/p/mstr-part-2, but I want to focus on legendary short seller James Chanos’ current trade wherein he buys bitcoin (via ETF) and shorts MSTR, in essence to “be like Mike” Saylor who sells MSTR shares at the market and uses them to add bitcoin to the company’s balance sheet. After all, if it’s good enough for Saylor, why shouldn’t everyone be doing it — shorting a company whose stock price is more than 2x its bitcoin holdings and using the proceeds to buy the bitcoin itself?
Saylor himself has said selling shares at 2x NAV (net asset value) to buy bitcoin is like selling dollars for two dollars each, and Chanos has apparently decided to get in while the getting (market cap more than 2x net asset value) is good. If the price of bitcoin moons, sending MSTR’s shares up, you are more than hedged in that event, too. At least that’s the theory.
The problem with this bet against MSTR’s mNAV, i.e., you are betting MSTR’s market cap will converge 1:1 toward its NAV in the short and medium term is this trade does not exist in a vacuum. Saylor has described how his ATM’s (at the market) sales of shares are accretive in BTC per share because of this very premium they carry. Yes, we’ll dilute your shares of the company, but because we’re getting you 2x the bitcoin per share, you are getting an ever smaller slice of an ever bigger overall pie, and the pie is growing 2x faster than your slice is reducing. (I https://www.chrisliss.com/p/mstr how this works in my first post.)
But for this accretion to continue, there must be a constant supply of “greater fools” to pony up for the infinitely printable shares which contain only half their value in underlying bitcoin. Yes, those shares will continue to accrete more BTC per share, but only if there are more fools willing to make this trade in the future. So will there be a constant supply of such “fools” to keep fueling MSTR’s mNAV multiple indefinitely?
Yes, there will be in my opinion because you have to look at the trade from the prospective fools’ perspective. Those “fools” are not trading bitcoin for MSTR, they are trading their dollars, selling other equities to raise them maybe, but in the end it’s a dollars for shares trade. They are not selling bitcoin for them.
You might object that those same dollars could buy bitcoin instead, so they are surely trading the opportunity cost of buying bitcoin for them, but if only 5-10 percent of the market (or less) is buying bitcoin itself, the bucket in which which those “fools” reside is the entire non-bitcoin-buying equity market. (And this is not considering the even larger debt market which Saylor has yet to tap in earnest.)
So for those 90-95 percent who do not and are not presently planning to own bitcoin itself, is buying MSTR a fool’s errand, so to speak? Not remotely. If MSTR shares are infinitely printable ATM, they are still less so than the dollar and other fiat currencies. And MSTR shares are backed 2:1 by bitcoin itself, while the fiat currencies are backed by absolutely nothing. So if you hold dollars or euros, trading them for MSTR shares is an errand more sage than foolish.
That’s why this trade (buying BTC and shorting MSTR) is so dangerous. Not only are there many people who won’t buy BTC buying MSTR, there are many funds and other investment entities who are only able to buy MSTR.
Do you want to get BTC at 1:1 with the 5-10 percent or MSTR backed 2:1 with the 90-95 percent. This is a bit like medical tests that have a 95 percent accuracy rate for an asymptomatic disease that only one percent of the population has. If someone tests positive, it’s more likely to be a false one than an indication he has the disease*. The accuracy rate, even at 19:1, is subservient to the size of the respective populations.
At some point this will no longer be the case, but so long as the understanding of bitcoin is not widespread, so long as the dollar is still the unit of account, the “greater fools” buying MSTR are still miles ahead of the greatest fools buying neither, and the stock price and mNAV should only increase.
. . .
One other thought: it’s more work to play defense than offense because the person on offense knows where he’s going, and the defender can only react to him once he moves. Similarly, Saylor by virtue of being the issuer of the shares knows when more will come online while Chanos and other short sellers are borrowing them to sell in reaction to Saylor’s strategy. At any given moment, Saylor can pause anytime, choosing to issue convertible debt or preferred shares with which to buy more bitcoin, and the shorts will not be given advance notice.
If the price runs, and there is no ATM that week because Saylor has stopped on a dime, so to speak, the shorts will be left having to scramble to change directions and buy the shares back to cover. Their momentum might be in the wrong direction, though, and like Allen Iverson breaking ankles with a crossover, Saylor might trigger a massive short squeeze, rocketing the share price ever higher. That’s why he actually welcomes Chanos et al trying this copycat strategy — it becomes the fuel for outsized gains.
For that reason, news that Chanos is shorting MSTR has not shaken my conviction, though there are other more pertinent https://www.chrisliss.com/p/mstr-part-2 with MSTR, of which one should be aware. And as always, do your own due diligence before investing in anything.
* To understand this, consider a population of 100,000, with one percent having a disease. That means 1,000 have it, 99,000 do not. If the test is 95 percent accurate, and everyone is tested, 950 of the 1,000 will test positive (true positives), 50 who have it will test negative (false negatives.) Of the positives, 95 percent of 99,000 (94,050) will test negative (true negatives) and five percent (4,950) will test positive (false positives). That means 4,950 out of 5,900 positives (84%) will be false.
-
 @ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03
@ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:51:54
@ 04c915da:3dfbecc9
2025-05-16 17:51:54In much of the world, it is incredibly difficult to access U.S. dollars. Local currencies are often poorly managed and riddled with corruption. Billions of people demand a more reliable alternative. While the dollar has its own issues of corruption and mismanagement, it is widely regarded as superior to the fiat currencies it competes with globally. As a result, Tether has found massive success providing low cost, low friction access to dollars. Tether claims 400 million total users, is on track to add 200 million more this year, processes 8.1 million transactions daily, and facilitates $29 billion in daily transfers. Furthermore, their estimates suggest nearly 40% of users rely on it as a savings tool rather than just a transactional currency.
Tether’s rise has made the company a financial juggernaut. Last year alone, Tether raked in over $13 billion in profit, with a lean team of less than 100 employees. Their business model is elegantly simple: hold U.S. Treasuries and collect the interest. With over $113 billion in Treasuries, Tether has turned a straightforward concept into a profit machine.
Tether’s success has resulted in many competitors eager to claim a piece of the pie. This has triggered a massive venture capital grift cycle in USD tokens, with countless projects vying to dethrone Tether. Due to Tether’s entrenched network effect, these challengers face an uphill battle with little realistic chance of success. Most educated participants in the space likely recognize this reality but seem content to perpetuate the grift, hoping to cash out by dumping their equity positions on unsuspecting buyers before they realize the reality of the situation.
Historically, Tether’s greatest vulnerability has been U.S. government intervention. For over a decade, the company operated offshore with few allies in the U.S. establishment, making it a major target for regulatory action. That dynamic has shifted recently and Tether has seized the opportunity. By actively courting U.S. government support, Tether has fortified their position. This strategic move will likely cement their status as the dominant USD token for years to come.
While undeniably a great tool for the millions of users that rely on it, Tether is not without flaws. As a centralized, trusted third party, it holds the power to freeze or seize funds at its discretion. Corporate mismanagement or deliberate malpractice could also lead to massive losses at scale. In their goal of mitigating regulatory risk, Tether has deepened ties with law enforcement, mirroring some of the concerns of potential central bank digital currencies. In practice, Tether operates as a corporate CBDC alternative, collaborating with authorities to surveil and seize funds. The company proudly touts partnerships with leading surveillance firms and its own data reveals cooperation in over 1,000 law enforcement cases, with more than $2.5 billion in funds frozen.
The global demand for Tether is undeniable and the company’s profitability reflects its unrivaled success. Tether is owned and operated by bitcoiners and will likely continue to push forward strategic goals that help the movement as a whole. Recent efforts to mitigate the threat of U.S. government enforcement will likely solidify their network effect and stifle meaningful adoption of rival USD tokens or CBDCs. Yet, for all their achievements, Tether is simply a worse form of money than bitcoin. Tether requires trust in a centralized entity, while bitcoin can be saved or spent without permission. Furthermore, Tether is tied to the value of the US Dollar which is designed to lose purchasing power over time, while bitcoin, as a truly scarce asset, is designed to increase in purchasing power with adoption. As people awaken to the risks of Tether’s control, and the benefits bitcoin provides, bitcoin adoption will likely surpass it.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:59:23
@ 04c915da:3dfbecc9
2025-05-16 17:59:23Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ 86dfbe73:628cef55
2025-05-25 08:20:07
@ 86dfbe73:628cef55
2025-05-25 08:20:07Robustheit ist die Eigenschaft eines Systems, auch unter schwierigen Bedingungen funktionieren zu können: trotz Störungen und einer gewissen Verschlechterung seiner internen Prozesse. Das Leben als Ganzes ist robust. Dasselbe gilt für Ökosysteme: Sie können den Verlust einiger Arten überstehen und sich an veränderte Umweltbedingungen anpassen.
Der Hauptfeind der Robustheit ist das Streben nach Effizienz. Ein auf Effizienz optimiertes System hat keine Reserven mehr, sich an Störungen anzupassen. Es wird fragil. Wir optimieren die Gesellschaft und ihre Subsysteme (z. B. Institutionen) seit 5000 Jahren auf Wachstum, Effizienz und Produktivität. Und wir haben das Optimierungstempo mit den beiden Turbo-Boosts fossile Brennstoffe und Informationstechnologie beschleunigt. Deshalb ist alles um uns herum fragil geworden. Beispielsweise kann ein Virusausbruch in China sich zu einer Pandemie entwickeln, weil die Menschen weit und schnell reisen können und müssen.
Robustheit ist nicht absolut und dauerhaft. Ein System kann durch Störungen, die zu gravierend für es sind, fragil werden. Ehemals robuste Ökosysteme wie Regenwälder wurden durch menschliche Ausbeutung fragil. Deregulierung hat sowohl Regierungen als auch die Wirtschaft effizienter gemacht, allerdings zum Preis zunehmender Fragilität. Unternehmen sind mächtiger geworden als viele Staaten, was bedeutet, dass demokratisch gewählte Parlamente und Regierungen nicht mehr die Kontrolle haben. Heute kann eine einzelne Person demokratische Wahlen weltweit manipulieren, indem sie ein soziales Netzwerk kontrolliert. Das ist Fragilität pur.
Wir müssen als Gesellschaft die Effizienz in den Hintergrund rücken und uns mehr auf Robustheit konzentrieren.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:12:05
@ 04c915da:3dfbecc9
2025-05-16 17:12:05One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ a5ee4475:2ca75401
2025-05-15 14:44:45
@ a5ee4475:2ca75401
2025-05-15 14:44:45lista #descentralismo #compilado #portugues
*Algumas destas listas ainda estão sendo trocadas, portanto as versões mais recentes delas só estão visíveis no Amethyst por causa da ferramenta de edição.
Clients do Nostr e Outras Coisas
nostr:naddr1qq245dz5tqe8w46swpphgmr4f3047s6629t45qg4waehxw309aex2mrp0yhxgctdw4eju6t09upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4guxde6sl
Modelos de IA e Ferramentas
nostr:naddr1qq24xwtyt9v5wjzefe6523j32dy5ga65gagkjqgswaehxw309ahx7um5wghx6mmd9upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4guk62czu
Iniciativas de Bitcoin
nostr:naddr1qvzqqqr4gupzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqq2nvmn5va9x2nrxfd2k5smyf3ux7vesd9znyqxygt4
Profissionais Brasileiros no Nostr
nostr:naddr1qq24qmnkwe6y67zlxgc4sumrxpxxce3kf9fn2qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7q3q5hhygatg5gmjyfkkguqn54f9r6k8m5m6ksyqffgjrf3uut982sqsxpqqqp65wp8uedu
Comunidades em Português no Nostr
nostr:naddr1qq2hwcejv4ykgdf3v9gxykrxfdqk753jxcc4gqg4waehxw309aex2mrp0yhxgctdw4eju6t09upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4gu455fm3
Grupos em Português no Nostr
nostr:nevent1qqs98kldepjmlxngupsyth40n0h5lw7z5ut5w4scvh27alc0w86tevcpzpmhxue69uhkummnw3ezumt0d5hsygy7fff8g6l23gp5uqtuyqwkqvucx6mhe7r9h7v6wyzzj0v6lrztcspsgqqqqqqs3ndneh
Jogos de Código Aberto
Open Source Games nostr:naddr1qvzqqqr4gupzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqq2kvwp3v4hhvk2sw3j5sm6h23g5wkz5ddzhz8x40v0
Itens Úteis com Esquemas Disponíveis
nostr:naddr1qqgrqvp5vd3kycejxask2efcv4jr2qgswaehxw309ahx7um5wghx6mmd9upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4guc43v6c
Formatação de Texto em Markdown
(Amethyst, Yakihone e outros) nostr:naddr1qvzqqqr4gupzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqq2454m8dfzn26z4f34kvu6fw4rysnrjxfm42wfpe90
Outros Links
nostr:nevent1qqsrm6ywny5r7ajakpppp0lt525n0s33x6tyn6pz0n8ws8k2tqpqracpzpmhxue69uhkummnw3ezumt0d5hsygp6e5ns0nv3dun430jky25y4pku6ylz68rz6zs7khv29q6rj5peespsgqqqqqqsmfwa78
-
 @ 21335073:a244b1ad
2025-05-09 13:56:57
@ 21335073:a244b1ad
2025-05-09 13:56:57Someone asked for my thoughts, so I’ll share them thoughtfully. I’m not here to dictate how to promote Nostr—I’m still learning about it myself. While I’m not new to Nostr, freedom tech is a newer space for me. I’m skilled at advocating for topics I deeply understand, but freedom tech isn’t my expertise, so take my words with a grain of salt. Nothing I say is set in stone.
Those who need Nostr the most are the ones most vulnerable to censorship on other platforms right now. Reaching them requires real-time awareness of global issues and the dynamic relationships between governments and tech providers, which can shift suddenly. Effective Nostr promoters must grasp this and adapt quickly.
The best messengers are people from or closely tied to these at-risk regions—those who truly understand the local political and cultural dynamics. They can connect with those in need when tensions rise. Ideal promoters are rational, trustworthy, passionate about Nostr, but above all, dedicated to amplifying people’s voices when it matters most.
Forget influencers, corporate-backed figures, or traditional online PR—it comes off as inauthentic, corny, desperate and forced. Nostr’s promotion should be grassroots and organic, driven by a few passionate individuals who believe in Nostr and the communities they serve.
The idea that “people won’t join Nostr due to lack of reach” is nonsense. Everyone knows X’s “reach” is mostly with bots. If humans want real conversations, Nostr is the place. X is great for propaganda, but Nostr is for the authentic voices of the people.
Those spreading Nostr must be so passionate they’re willing to onboard others, which is time-consuming but rewarding for the right person. They’ll need to make Nostr and onboarding a core part of who they are. I see no issue with that level of dedication. I’ve been known to get that way myself at times. It’s fun for some folks.
With love, I suggest not adding Bitcoin promotion with Nostr outreach. Zaps already integrate that element naturally. (Still promote within the Bitcoin ecosystem, but this is about reaching vulnerable voices who needed Nostr yesterday.)
To promote Nostr, forget conventional strategies. “Influencers” aren’t the answer. “Influencers” are not the future. A trusted local community member has real influence—reach them. Connect with people seeking Nostr’s benefits but lacking the technical language to express it. This means some in the Nostr community might need to step outside of the Bitcoin bubble, which is uncomfortable but necessary. Thank you in advance to those who are willing to do that.
I don’t know who is paid to promote Nostr, if anyone. This piece isn’t shade. But it’s exhausting to see innocent voices globally silenced on corporate platforms like X while Nostr exists. Last night, I wondered: how many more voices must be censored before the Nostr community gets uncomfortable and thinks creatively to reach the vulnerable?
A warning: the global need for censorship-resistant social media is undeniable. If Nostr doesn’t make itself known, something else will fill that void. Let’s start this conversation.
-
 @ 088436cd:9d2646cc
2025-05-01 21:01:55
@ 088436cd:9d2646cc
2025-05-01 21:01:55The arrival of the coronavirus brought not only illness and death but also fear and panic. In such an environment of uncertainty, people have naturally stocked up on necessities, not knowing when things will return to normal.
Retail shelves have been cleared out, and even online suppliers like Amazon and Walmart are out of stock for some items. Independent sellers on these e-commerce platforms have had to fill the gap. With the huge increase in demand, they have found that their inventory has skyrocketed in value.
Many in need of these items (e.g. toilet paper, hand sanitizer and masks) balk at the new prices. They feel they are being taken advantage of in a time of need and call for intervention by the government to lower prices. The government has heeded that call, labeling the independent sellers as "price gougers" and threatening sanctions if they don't lower their prices. Amazon has suspended seller accounts and law enforcement at all levels have threatened to prosecute. Prices have dropped as a result and at first glance this seems like a victory for fair play. But, we will have to dig deeper to understand the unseen consequences of this intervention.
We must look at the economics of the situation, how supply and demand result in a price and how that price acts as a signal that goes out to everyone, informing them of underlying conditions in the economy and helping coordinate their actions.
It all started with a rise in demand. Given a fixed supply (e.g., the limited stock on shelves and in warehouses), an increase in demand inevitably leads to higher prices. Most people are familiar with this phenomenon, such as paying more for airline tickets during holidays or surge pricing for rides.
Higher prices discourage less critical uses of scarce resources. For example, you might not pay $1,000 for a plane ticket to visit your aunt if you can get one for $100 the following week, but someone else might pay that price to visit a dying relative. They value that plane seat more than you.
*** During the crisis, demand surged and their shelves emptied even though
However, retail outlets have not raised prices. They have kept them low, so the low-value uses of things like toilet paper, masks and hand sanitizer has continued. Often, this "use" just takes the form of hoarding. At everyday low prices, it makes sense to buy hundreds of rolls and bottles. You know you will use them eventually, so why not stock up? And, with all those extra supplies in the closet and basement, you don't need to change your behavior much. You don't have to ration your use.
At the low prices, these scarce resources got bought up faster and faster until there was simply none left. The reality of the situation became painfully clear to those who didn't panic and got to the store late: You have no toilet paper and you're not going to any time soon.
However, if prices had been allowed to rise, a number of effects would have taken place that would have coordinated the behavior of everyone so that valuable resources would not have been wasted or hoarded, and everyone could have had access to what they needed.
On the demand side, if prices had been allowed to rise, people would have begun to self-ration. You might leave those extra plies on the roll next time if you know they will cost ten times as much to replace. Or, you might choose to clean up a spill with a rag rather than disposable tissue. Most importantly, you won't hoard as much. That 50th bottle of hand sanitizer might just not be worth it at the new, high price. You'll leave it on the shelf for someone else who may have none.
On the supply side, higher prices would have incentivized people to offer up more of their stockpiles for sale. If you have a pallet full of toilet paper in your basement and all of the sudden they are worth $15 per roll, you might just list a few online. But, if it is illegal to do so, you probably won't.
Imagine you run a business installing insulation and have a few thousand respirator masks on hand for your employees. During a pandemic, it is much more important that people breathe filtered air than that insulation get installed, and that fact is reflected in higher prices. You will sell your extra masks at the higher price rather than store them for future insulation jobs, and the scarce resource will be put to its most important use.
Producers of hand sanitizer would go into overdrive if prices were allowed to rise. They would pay their employees overtime, hire new ones, and pay a premium for their supplies, making sure their raw materials don't go to less important uses.
These kinds of coordinated actions all across the economy would be impossible without real prices to guide them. How do you know if it makes sense to spend an extra $10k bringing a thousand masks to market unless you know you can get more than $10 per mask? If the price is kept artificially low, you simply can't do it. The money just isn't there.
These are the immediate effects of a price change, but incredibly, price changes also coordinate people's actions across space and time.
Across space, there are different supply and demand conditions in different places, and thus prices are not uniform. We know some places are real "hot spots" for the virus, while others are mostly unaffected. High demand in the hot spots leads to higher prices there, which attracts more of the resource to those areas. Boxes and boxes of essential items would pour in where they are needed most from where they are needed least, but only if prices were allowed to adjust freely.
This would be accomplished by individuals and businesses buying low in the unaffected areas, selling high in the hot spots and subtracting their labor and transportation costs from the difference. Producers of new supply would know exactly where it is most needed and ship to the high-demand, high-price areas first. The effect of these actions is to increase prices in the low demand areas and reduce them in the high demand areas. People in the low demand areas will start to self-ration more, reflecting the reality of their neighbors, and people in the hotspots will get some relief.
However, by artificially suppressing prices in the hot spot, people there will simply buy up the available supply and run out, and it will be cost prohibitive to bring in new supply from low-demand areas.
Prices coordinate economic actions across time as well. Just as entrepreneurs and businesses can profit by transporting scarce necessities from low-demand to high-demand areas, they can also profit by buying in low-demand times and storing their merchandise for when it is needed most.
Just as allowing prices to freely adjust in one area relative to another will send all the right signals for the optimal use of a scarce resource, allowing prices to freely adjust over time will do the same.
When an entrepreneur buys up resources during low-demand times in anticipation of a crisis, she restricts supply ahead of the crisis, which leads to a price increase. She effectively bids up the price. The change in price affects consumers and producers in all the ways mentioned above. Consumers self-ration more, and producers bring more of the resource to market.
Our entrepreneur has done a truly incredible thing. She has predicted the future, and by so doing has caused every individual in the economy to prepare for a shortage they don't even know is coming! And, by discouraging consumption and encouraging production ahead of time, she blunts the impact the crisis will have. There will be more of the resource to go around when it is needed most.
On top of this, our entrepreneur still has her stockpile she saved back when everyone else was blithely using it up. She can now further mitigate the damage of the crisis by selling her stock during the worst of it, when people are most desperate for relief. She will know when this is because the price will tell her, but only if it is allowed to adjust freely. When the price is at its highest is when people need the resource the most, and those willing to pay will not waste it or hoard it. They will put it to its highest valued use.
The economy is like a big bus we are all riding in, going down a road with many twists and turns. Just as it is difficult to see into the future, it is difficult to see out the bus windows at the road ahead.
On the dashboard, we don't have a speedometer or fuel gauge. Instead we have all the prices for everything in the economy. Prices are what tell us the condition of the bus and the road. They tell us everything. Without them, we are blind.
Good times are a smooth road. Consumer prices and interest rates are low, investment returns are steady. We hit the gas and go fast. But, the road is not always straight and smooth. Sometimes there are sharp turns and rough patches. Successful entrepreneurs are the ones who can see what is coming better than everyone else. They are our navigators.
When they buy up scarce resources ahead of a crisis, they are hitting the brakes and slowing us down. When they divert resources from one area to another, they are steering us onto a smoother path. By their actions in the market, they adjust the prices on our dashboard to reflect the conditions of the road ahead, so we can prepare for, navigate and get through the inevitable difficulties we will face.
Interfering with the dashboard by imposing price floors or price caps doesn't change the conditions of the road (the number of toilet paper rolls in existence hasn't changed). All it does is distort our perception of those conditions. We think the road is still smooth--our heavy foot stomping the gas--as we crash onto a rocky dirt road at 80 miles per hour (empty shelves at the store for weeks on end).
Supply, demand and prices are laws of nature. All of this is just how things work. It isn't right or wrong in a moral sense. Price caps lead to waste, shortages and hoarding as surely as water flows downhill. The opposite--allowing prices to adjust freely--leads to conservation of scarce resources and their being put to their highest valued use. And yes, it leads to profits for the entrepreneurs who were able to correctly predict future conditions, and losses for those who weren't.
Is it fair that they should collect these profits? On the one hand, anyone could have stocked up on toilet paper, hand sanitizer and face masks at any time before the crisis, so we all had a fair chance to get the supplies cheaply. On the other hand, it just feels wrong that some should profit so much at a time when there is so much need.
Our instinct in the moment is to see the entrepreneur as a villain, greedy "price gouger". But we don't see the long chain of economic consequences the led to the situation we feel is unfair.
If it weren't for anti-price-gouging laws, the major retailers would have raised their prices long before the crisis became acute. When they saw demand outstrip supply, they would have raised prices, not by 100 fold, but gradually and long before anyone knew how serious things would have become. Late comers would have had to pay more, but at least there would be something left on the shelf.
As an entrepreneur, why take risks trying to anticipate the future if you can't reap the reward when you are right? Instead of letting instead of letting entrepreneurs--our navigators--guide us, we are punishing and vilifying them, trying to force prices to reflect a reality that simply doesn't exist.
In a crisis, more than any other time, prices must be allowed to fluctuate. To do otherwise is to blind ourselves at a time when danger and uncertainty abound. It is economic suicide.
In a crisis, there is great need, and the way to meet that need is not by pretending it's not there, by forcing prices to reflect a world where there isn't need. They way to meet the need is the same it has always been, through charity.
If the people in government want to help, the best way for the to do so is to be charitable and reduce their taxes and fees as much as possible, ideally to zero in a time of crisis. Amazon, for example, could instantly reduce the price of all crisis related necessities by 20% if they waived their fee. This would allow for more uses by more people of these scarce supplies as hoarders release their stockpiles on to the market, knowing they can get 20% more for their stock. Governments could reduce or eliminate their tax burden on high-demand, crisis-related items and all the factors that go into their production, with the same effect: a reduction in prices and expansion of supply. All of us, including the successful entrepreneurs and the wealthy for whom high prices are not a great burden, could donate to relief efforts.
These ideas are not new or untested. This is core micro economics. It has been taught for hundreds of years in universities the world over. The fact that every crisis that comes along stirs up ire against entrepreneurs indicates not that the economics is wrong, but that we have a strong visceral reaction against what we perceive to be unfairness. This is as it should be. Unfairness is wrong and the anger it stirs in us should compel us to right the wrong. Our anger itself isn't wrong, it's just misplaced.
Entrepreneurs didn't cause the prices to rise. Our reaction to a virus did that. We saw a serious threat and an uncertain future and followed our natural impulse to hoard. Because prices at major retail suppliers didn't rise, that impulse ran rampant and we cleared the shelves until there was nothing left. We ran the bus right off the road and them blamed the entrepreneurs for showing us the reality of our situation, for shaking us out of the fantasy of low prices.
All of this is not to say that entrepreneurs are high-minded public servants. They are just doing their job. Staking your money on an uncertain future is a risky business. There are big risks and big rewards. Most entrepreneurs just scrape by or lose their capital in failed ventures.
However, the ones that get it right must be allowed to keep their profits, or else no one will try and we'll all be driving blind. We need our navigators. It doesn't even matter if they know all the positive effects they are having on the rest of us and the economy as a whole. So long as they are buying low and selling high--so long as they are doing their job--they will be guiding the rest of us through the good times and the bad, down the open road and through the rough spots.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ a39d19ec:3d88f61e
2025-04-22 12:44:42
@ a39d19ec:3d88f61e
2025-04-22 12:44:42Die Debatte um Migration, Grenzsicherung und Abschiebungen wird in Deutschland meist emotional geführt. Wer fordert, dass illegale Einwanderer abgeschoben werden, sieht sich nicht selten dem Vorwurf des Rassismus ausgesetzt. Doch dieser Vorwurf ist nicht nur sachlich unbegründet, sondern verkehrt die Realität ins Gegenteil: Tatsächlich sind es gerade diejenigen, die hinter jeder Forderung nach Rechtssicherheit eine rassistische Motivation vermuten, die selbst in erster Linie nach Hautfarbe, Herkunft oder Nationalität urteilen.
Das Recht steht über Emotionen
Deutschland ist ein Rechtsstaat. Das bedeutet, dass Regeln nicht nach Bauchgefühl oder politischer Stimmungslage ausgelegt werden können, sondern auf klaren gesetzlichen Grundlagen beruhen müssen. Einer dieser Grundsätze ist in Artikel 16a des Grundgesetzes verankert. Dort heißt es:
„Auf Absatz 1 [Asylrecht] kann sich nicht berufen, wer aus einem Mitgliedstaat der Europäischen Gemeinschaften oder aus einem anderen Drittstaat einreist, in dem die Anwendung des Abkommens über die Rechtsstellung der Flüchtlinge und der Europäischen Menschenrechtskonvention sichergestellt ist.“
Das bedeutet, dass jeder, der über sichere Drittstaaten nach Deutschland einreist, keinen Anspruch auf Asyl hat. Wer dennoch bleibt, hält sich illegal im Land auf und unterliegt den geltenden Regelungen zur Rückführung. Die Forderung nach Abschiebungen ist daher nichts anderes als die Forderung nach der Einhaltung von Recht und Gesetz.
Die Umkehrung des Rassismusbegriffs
Wer einerseits behauptet, dass das deutsche Asyl- und Aufenthaltsrecht strikt durchgesetzt werden soll, und andererseits nicht nach Herkunft oder Hautfarbe unterscheidet, handelt wertneutral. Diejenigen jedoch, die in einer solchen Forderung nach Rechtsstaatlichkeit einen rassistischen Unterton sehen, projizieren ihre eigenen Denkmuster auf andere: Sie unterstellen, dass die Debatte ausschließlich entlang ethnischer, rassistischer oder nationaler Kriterien geführt wird – und genau das ist eine rassistische Denkweise.
Jemand, der illegale Einwanderung kritisiert, tut dies nicht, weil ihn die Herkunft der Menschen interessiert, sondern weil er den Rechtsstaat respektiert. Hingegen erkennt jemand, der hinter dieser Kritik Rassismus wittert, offenbar in erster Linie die „Rasse“ oder Herkunft der betreffenden Personen und reduziert sie darauf.
Finanzielle Belastung statt ideologischer Debatte
Neben der rechtlichen gibt es auch eine ökonomische Komponente. Der deutsche Wohlfahrtsstaat basiert auf einem Solidarprinzip: Die Bürger zahlen in das System ein, um sich gegenseitig in schwierigen Zeiten zu unterstützen. Dieser Wohlstand wurde über Generationen hinweg von denjenigen erarbeitet, die hier seit langem leben. Die Priorität liegt daher darauf, die vorhandenen Mittel zuerst unter denjenigen zu verteilen, die durch Steuern, Sozialabgaben und Arbeit zum Erhalt dieses Systems beitragen – nicht unter denen, die sich durch illegale Einreise und fehlende wirtschaftliche Eigenleistung in das System begeben.
Das ist keine ideologische Frage, sondern eine rein wirtschaftliche Abwägung. Ein Sozialsystem kann nur dann nachhaltig funktionieren, wenn es nicht unbegrenzt belastet wird. Würde Deutschland keine klaren Regeln zur Einwanderung und Abschiebung haben, würde dies unweigerlich zur Überlastung des Sozialstaates führen – mit negativen Konsequenzen für alle.
Sozialpatriotismus
Ein weiterer wichtiger Aspekt ist der Schutz der Arbeitsleistung jener Generationen, die Deutschland nach dem Zweiten Weltkrieg mühsam wieder aufgebaut haben. Während oft betont wird, dass die Deutschen moralisch kein Erbe aus der Zeit vor 1945 beanspruchen dürfen – außer der Verantwortung für den Holocaust –, ist es umso bedeutsamer, das neue Erbe nach 1945 zu respektieren, das auf Fleiß, Disziplin und harter Arbeit beruht. Der Wiederaufbau war eine kollektive Leistung deutscher Menschen, deren Früchte nicht bedenkenlos verteilt werden dürfen, sondern vorrangig denjenigen zugutekommen sollten, die dieses Fundament mitgeschaffen oder es über Generationen mitgetragen haben.
Rechtstaatlichkeit ist nicht verhandelbar
Wer sich für eine konsequente Abschiebepraxis ausspricht, tut dies nicht aus rassistischen Motiven, sondern aus Respekt vor der Rechtsstaatlichkeit und den wirtschaftlichen Grundlagen des Landes. Der Vorwurf des Rassismus in diesem Kontext ist daher nicht nur falsch, sondern entlarvt eine selektive Wahrnehmung nach rassistischen Merkmalen bei denjenigen, die ihn erheben.
-
 @ 4ba8e86d:89d32de4
2025-04-21 02:13:56
@ 4ba8e86d:89d32de4
2025-04-21 02:13:56Tutorial feito por nostr:nostr:npub1rc56x0ek0dd303eph523g3chm0wmrs5wdk6vs0ehd0m5fn8t7y4sqra3tk poste original abaixo:
Parte 1 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/263585/tutorial-debloat-de-celulares-android-via-adb-parte-1
Parte 2 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/index.php/263586/tutorial-debloat-de-celulares-android-via-adb-parte-2
Quando o assunto é privacidade em celulares, uma das medidas comumente mencionadas é a remoção de bloatwares do dispositivo, também chamado de debloat. O meio mais eficiente para isso sem dúvidas é a troca de sistema operacional. Custom Rom’s como LineageOS, GrapheneOS, Iodé, CalyxOS, etc, já são bastante enxutos nesse quesito, principalmente quanto não é instalado os G-Apps com o sistema. No entanto, essa prática pode acabar resultando em problemas indesejados como a perca de funções do dispositivo, e até mesmo incompatibilidade com apps bancários, tornando este método mais atrativo para quem possui mais de um dispositivo e separando um apenas para privacidade. Pensando nisso, pessoas que possuem apenas um único dispositivo móvel, que são necessitadas desses apps ou funções, mas, ao mesmo tempo, tem essa visão em prol da privacidade, buscam por um meio-termo entre manter a Stock rom, e não ter seus dados coletados por esses bloatwares. Felizmente, a remoção de bloatwares é possível e pode ser realizada via root, ou mais da maneira que este artigo irá tratar, via adb.
O que são bloatwares?
Bloatware é a junção das palavras bloat (inchar) + software (programa), ou seja, um bloatware é basicamente um programa inútil ou facilmente substituível — colocado em seu dispositivo previamente pela fabricante e operadora — que está no seu dispositivo apenas ocupando espaço de armazenamento, consumindo memória RAM e pior, coletando seus dados e enviando para servidores externos, além de serem mais pontos de vulnerabilidades.
O que é o adb?
O Android Debug Brigde, ou apenas adb, é uma ferramenta que se utiliza das permissões de usuário shell e permite o envio de comandos vindo de um computador para um dispositivo Android exigindo apenas que a depuração USB esteja ativa, mas também pode ser usada diretamente no celular a partir do Android 11, com o uso do Termux e a depuração sem fio (ou depuração wifi). A ferramenta funciona normalmente em dispositivos sem root, e também funciona caso o celular esteja em Recovery Mode.
Requisitos:
Para computadores:
• Depuração USB ativa no celular; • Computador com adb; • Cabo USB;
Para celulares:
• Depuração sem fio (ou depuração wifi) ativa no celular; • Termux; • Android 11 ou superior;
Para ambos:
• Firewall NetGuard instalado e configurado no celular; • Lista de bloatwares para seu dispositivo;
Ativação de depuração:
Para ativar a Depuração USB em seu dispositivo, pesquise como ativar as opções de desenvolvedor de seu dispositivo, e lá ative a depuração. No caso da depuração sem fio, sua ativação irá ser necessária apenas no momento que for conectar o dispositivo ao Termux.
Instalação e configuração do NetGuard
O NetGuard pode ser instalado através da própria Google Play Store, mas de preferência instale pela F-Droid ou Github para evitar telemetria.
F-Droid: https://f-droid.org/packages/eu.faircode.netguard/
Github: https://github.com/M66B/NetGuard/releases
Após instalado, configure da seguinte maneira:
Configurações → padrões (lista branca/negra) → ative as 3 primeiras opções (bloquear wifi, bloquear dados móveis e aplicar regras ‘quando tela estiver ligada’);
Configurações → opções avançadas → ative as duas primeiras (administrar aplicativos do sistema e registrar acesso a internet);
Com isso, todos os apps estarão sendo bloqueados de acessar a internet, seja por wifi ou dados móveis, e na página principal do app basta permitir o acesso a rede para os apps que você vai usar (se necessário). Permita que o app rode em segundo plano sem restrição da otimização de bateria, assim quando o celular ligar, ele já estará ativo.
Lista de bloatwares
Nem todos os bloatwares são genéricos, haverá bloatwares diferentes conforme a marca, modelo, versão do Android, e até mesmo região.
Para obter uma lista de bloatwares de seu dispositivo, caso seu aparelho já possua um tempo de existência, você encontrará listas prontas facilmente apenas pesquisando por elas. Supondo que temos um Samsung Galaxy Note 10 Plus em mãos, basta pesquisar em seu motor de busca por:
Samsung Galaxy Note 10 Plus bloatware listProvavelmente essas listas já terão inclusas todos os bloatwares das mais diversas regiões, lhe poupando o trabalho de buscar por alguma lista mais específica.
Caso seu aparelho seja muito recente, e/ou não encontre uma lista pronta de bloatwares, devo dizer que você acaba de pegar em merda, pois é chato para um caralho pesquisar por cada aplicação para saber sua função, se é essencial para o sistema ou se é facilmente substituível.
De antemão já aviso, que mais para frente, caso vossa gostosura remova um desses aplicativos que era essencial para o sistema sem saber, vai acabar resultando na perda de alguma função importante, ou pior, ao reiniciar o aparelho o sistema pode estar quebrado, lhe obrigando a seguir com uma formatação, e repetir todo o processo novamente.
Download do adb em computadores
Para usar a ferramenta do adb em computadores, basta baixar o pacote chamado SDK platform-tools, disponível através deste link: https://developer.android.com/tools/releases/platform-tools. Por ele, você consegue o download para Windows, Mac e Linux.
Uma vez baixado, basta extrair o arquivo zipado, contendo dentro dele uma pasta chamada platform-tools que basta ser aberta no terminal para se usar o adb.
Download do adb em celulares com Termux.
Para usar a ferramenta do adb diretamente no celular, antes temos que baixar o app Termux, que é um emulador de terminal linux, e já possui o adb em seu repositório. Você encontra o app na Google Play Store, mas novamente recomendo baixar pela F-Droid ou diretamente no Github do projeto.
F-Droid: https://f-droid.org/en/packages/com.termux/
Github: https://github.com/termux/termux-app/releases
Processo de debloat
Antes de iniciarmos, é importante deixar claro que não é para você sair removendo todos os bloatwares de cara sem mais nem menos, afinal alguns deles precisam antes ser substituídos, podem ser essenciais para você para alguma atividade ou função, ou até mesmo são insubstituíveis.
Alguns exemplos de bloatwares que a substituição é necessária antes da remoção, é o Launcher, afinal, é a interface gráfica do sistema, e o teclado, que sem ele só é possível digitar com teclado externo. O Launcher e teclado podem ser substituídos por quaisquer outros, minha recomendação pessoal é por aqueles que respeitam sua privacidade, como Pie Launcher e Simple Laucher, enquanto o teclado pelo OpenBoard e FlorisBoard, todos open-source e disponíveis da F-Droid.
Identifique entre a lista de bloatwares, quais você gosta, precisa ou prefere não substituir, de maneira alguma você é obrigado a remover todos os bloatwares possíveis, modifique seu sistema a seu bel-prazer. O NetGuard lista todos os apps do celular com o nome do pacote, com isso você pode filtrar bem qual deles não remover.
Um exemplo claro de bloatware insubstituível e, portanto, não pode ser removido, é o com.android.mtp, um protocolo onde sua função é auxiliar a comunicação do dispositivo com um computador via USB, mas por algum motivo, tem acesso a rede e se comunica frequentemente com servidores externos. Para esses casos, e melhor solução mesmo é bloquear o acesso a rede desses bloatwares com o NetGuard.
MTP tentando comunicação com servidores externos:
Executando o adb shell
No computador
Faça backup de todos os seus arquivos importantes para algum armazenamento externo, e formate seu celular com o hard reset. Após a formatação, e a ativação da depuração USB, conecte seu aparelho e o pc com o auxílio de um cabo USB. Muito provavelmente seu dispositivo irá apenas começar a carregar, por isso permita a transferência de dados, para que o computador consiga se comunicar normalmente com o celular.
Já no pc, abra a pasta platform-tools dentro do terminal, e execute o seguinte comando:
./adb start-serverO resultado deve ser:
daemon not running; starting now at tcp:5037 daemon started successfully
E caso não apareça nada, execute:
./adb kill-serverE inicie novamente.
Com o adb conectado ao celular, execute:
./adb shellPara poder executar comandos diretamente para o dispositivo. No meu caso, meu celular é um Redmi Note 8 Pro, codinome Begonia.
Logo o resultado deve ser:
begonia:/ $
Caso ocorra algum erro do tipo:
adb: device unauthorized. This adb server’s $ADB_VENDOR_KEYS is not set Try ‘adb kill-server’ if that seems wrong. Otherwise check for a confirmation dialog on your device.
Verifique no celular se apareceu alguma confirmação para autorizar a depuração USB, caso sim, autorize e tente novamente. Caso não apareça nada, execute o kill-server e repita o processo.
No celular
Após realizar o mesmo processo de backup e hard reset citado anteriormente, instale o Termux e, com ele iniciado, execute o comando:
pkg install android-toolsQuando surgir a mensagem “Do you want to continue? [Y/n]”, basta dar enter novamente que já aceita e finaliza a instalação
Agora, vá até as opções de desenvolvedor, e ative a depuração sem fio. Dentro das opções da depuração sem fio, terá uma opção de emparelhamento do dispositivo com um código, que irá informar para você um código em emparelhamento, com um endereço IP e porta, que será usado para a conexão com o Termux.
Para facilitar o processo, recomendo que abra tanto as configurações quanto o Termux ao mesmo tempo, e divida a tela com os dois app’s, como da maneira a seguir:
Para parear o Termux com o dispositivo, não é necessário digitar o ip informado, basta trocar por “localhost”, já a porta e o código de emparelhamento, deve ser digitado exatamente como informado. Execute:
adb pair localhost:porta CódigoDeEmparelhamentoDe acordo com a imagem mostrada anteriormente, o comando ficaria “adb pair localhost:41255 757495”.
Com o dispositivo emparelhado com o Termux, agora basta conectar para conseguir executar os comandos, para isso execute:
adb connect localhost:portaObs: a porta que você deve informar neste comando não é a mesma informada com o código de emparelhamento, e sim a informada na tela principal da depuração sem fio.
Pronto! Termux e adb conectado com sucesso ao dispositivo, agora basta executar normalmente o adb shell:
adb shellRemoção na prática Com o adb shell executado, você está pronto para remover os bloatwares. No meu caso, irei mostrar apenas a remoção de um app (Google Maps), já que o comando é o mesmo para qualquer outro, mudando apenas o nome do pacote.
Dentro do NetGuard, verificando as informações do Google Maps:
Podemos ver que mesmo fora de uso, e com a localização do dispositivo desativado, o app está tentando loucamente se comunicar com servidores externos, e informar sabe-se lá que peste. Mas sem novidades até aqui, o mais importante é que podemos ver que o nome do pacote do Google Maps é com.google.android.apps.maps, e para o remover do celular, basta executar:
pm uninstall –user 0 com.google.android.apps.mapsE pronto, bloatware removido! Agora basta repetir o processo para o resto dos bloatwares, trocando apenas o nome do pacote.
Para acelerar o processo, você pode já criar uma lista do bloco de notas com os comandos, e quando colar no terminal, irá executar um atrás do outro.
Exemplo de lista:
Caso a donzela tenha removido alguma coisa sem querer, também é possível recuperar o pacote com o comando:
cmd package install-existing nome.do.pacotePós-debloat
Após limpar o máximo possível o seu sistema, reinicie o aparelho, caso entre no como recovery e não seja possível dar reboot, significa que você removeu algum app “essencial” para o sistema, e terá que formatar o aparelho e repetir toda a remoção novamente, desta vez removendo poucos bloatwares de uma vez, e reiniciando o aparelho até descobrir qual deles não pode ser removido. Sim, dá trabalho… quem mandou querer privacidade?
Caso o aparelho reinicie normalmente após a remoção, parabéns, agora basta usar seu celular como bem entender! Mantenha o NetGuard sempre executando e os bloatwares que não foram possíveis remover não irão se comunicar com servidores externos, passe a usar apps open source da F-Droid e instale outros apps através da Aurora Store ao invés da Google Play Store.
Referências: Caso você seja um Australopithecus e tenha achado este guia difícil, eis uma videoaula (3:14:40) do Anderson do canal Ciberdef, realizando todo o processo: http://odysee.com/@zai:5/Como-remover-at%C3%A9-200-APLICATIVOS-que-colocam-a-sua-PRIVACIDADE-E-SEGURAN%C3%87A-em-risco.:4?lid=6d50f40314eee7e2f218536d9e5d300290931d23
Pdf’s do Anderson citados na videoaula: créditos ao anon6837264 http://eternalcbrzpicytj4zyguygpmkjlkddxob7tptlr25cdipe5svyqoqd.onion/file/3863a834d29285d397b73a4af6fb1bbe67c888d72d30/t-05e63192d02ffd.pdf
Processo de instalação do Termux e adb no celular: https://youtu.be/APolZrPHSms
-
 @ 08f96856:ffe59a09
2025-05-15 01:17:18
@ 08f96856:ffe59a09
2025-05-15 01:17:18เมื่อพูดถึง Bitcoin Standard หลายคนมักนึกถึงภาพโลกอนาคตที่ทุกคนใช้บิตคอยน์ซื้อกาแฟหรือของใช้ในชีวิตประจำวัน ภาพแบบนั้นดูเหมือนไกลตัวและเป็นไปไม่ได้ในความเป็นจริง หลายคนถึงกับพูดว่า “คงไม่ทันเห็นในช่วงชีวิตนี้หรอก” แต่ในมุมมองของผม Bitcoin Standard อาจไม่ได้เริ่มต้นจากการที่เราจ่ายบิตคอยน์โดยตรงในร้านค้า แต่อาจเริ่มจากบางสิ่งที่เงียบกว่า ลึกกว่า และเกิดขึ้นแล้วในขณะนี้ นั่นคือ การล่มสลายทีละน้อยของระบบเฟียตที่เราใช้กันอยู่
ระบบเงินที่อิงกับอำนาจรัฐกำลังเข้าสู่ช่วงขาลง รัฐบาลทั่วโลกกำลังจมอยู่ในภาระหนี้ระดับประวัติการณ์ แม้แต่ประเทศมหาอำนาจก็เริ่มแสดงสัญญาณของภาวะเสี่ยงผิดนัดชำระหนี้ อัตราเงินเฟ้อกลายเป็นปัญหาเรื้อรังที่ไม่มีท่าทีจะหายไป ธนาคารที่เคยโอนฟรีเริ่มกลับมาคิดค่าธรรมเนียม และประชาชนก็เริ่มรู้สึกถึงการเสื่อมศรัทธาในระบบการเงินดั้งเดิม แม้จะยังพูดกันไม่เต็มเสียงก็ตาม
ในขณะเดียวกัน บิตคอยน์เองก็กำลังพัฒนาแบบเงียบ ๆ เงียบ... แต่ไม่เคยหยุด โดยเฉพาะในระดับ Layer 2 ที่เริ่มแสดงศักยภาพอย่างจริงจัง Lightning Network เป็น Layer 2 ที่เปิดใช้งานมาได้ระยะเวลสหนึ่ง และยังคงมีบทบาทสำคัญที่สุดในระบบนิเวศของบิตคอยน์ มันทำให้การชำระเงินเร็วขึ้น มีต้นทุนต่ำ และไม่ต้องบันทึกทุกธุรกรรมลงบล็อกเชน เครือข่ายนี้กำลังขยายตัวทั้งในแง่ของโหนดและการใช้งานจริงทั่วโลก
ขณะเดียวกัน Layer 2 ทางเลือกอื่นอย่าง Ark Protocol ก็กำลังพัฒนาเพื่อตอบโจทย์ด้านความเป็นส่วนตัวและประสบการณ์ใช้งานที่ง่าย BitVM เปิดแนวทางใหม่ให้บิตคอยน์รองรับ smart contract ได้ในระดับ Turing-complete ซึ่งทำให้เกิดความเป็นไปได้ในกรณีใช้งานอีกมากมาย และเทคโนโลยีที่น่าสนใจอย่าง Taproot Assets, Cashu และ Fedimint ก็ทำให้การออกโทเคนหรือสกุลเงินที่อิงกับบิตคอยน์เป็นจริงได้บนโครงสร้างของบิตคอยน์เอง
เทคโนโลยีเหล่านี้ไม่ใช่การเติบโตแบบปาฏิหาริย์ แต่มันคืบหน้าอย่างต่อเนื่องและมั่นคง และนั่นคือเหตุผลที่มันจะ “อยู่รอด” ได้ในระยะยาว เมื่อฐานของความน่าเชื่อถือไม่ใช่บริษัท รัฐบาล หรือทุน แต่คือสิ่งที่ตรวจสอบได้และเปลี่ยนกฎไม่ได้
แน่นอนว่าบิตคอยน์ต้องแข่งขันกับ stable coin, เงินดิจิทัลของรัฐ และ cryptocurrency อื่น ๆ แต่สิ่งที่ทำให้มันเหนือกว่านั้นไม่ใช่ฟีเจอร์ หากแต่เป็นความทนทาน และความมั่นคงของกฎที่ไม่มีใครเปลี่ยนได้ ไม่มีทีมพัฒนา ไม่มีบริษัท ไม่มีประตูปิด หรือการยึดบัญชี มันยืนอยู่บนคณิตศาสตร์ พลังงาน และเวลา
หลายกรณีใช้งานที่เคยถูกทดลองในโลกคริปโตจะค่อย ๆ เคลื่อนเข้ามาสู่บิตคอยน์ เพราะโครงสร้างของมันแข็งแกร่งกว่า ไม่ต้องการทีมพัฒนาแกนกลาง ไม่ต้องพึ่งกลไกเสี่ยงต่อการผูกขาด และไม่ต้องการ “ความเชื่อใจ” จากใครเลย
Bitcoin Standard ที่ผมพูดถึงจึงไม่ใช่การเปลี่ยนแปลงแบบพลิกหน้ามือเป็นหลังมือ แต่คือการ “เปลี่ยนฐานของระบบ” ทีละชั้น ระบบการเงินใหม่ที่อิงอยู่กับบิตคอยน์กำลังเกิดขึ้นแล้ว มันไม่ใช่โลกที่ทุกคนถือเหรียญบิตคอยน์ แต่มันคือโลกที่คนใช้อาจไม่รู้ตัวด้วยซ้ำว่า “สิ่งที่เขาใช้นั้นอิงอยู่กับบิตคอยน์”
ผู้คนอาจใช้เงินดิจิทัลที่สร้างบน Layer 3 หรือ Layer 4 ผ่านแอป ผ่านแพลตฟอร์ม หรือผ่านสกุลเงินใหม่ที่ดูไม่ต่างจากเดิม แต่เบื้องหลังของระบบจะผูกไว้กับบิตคอยน์
และถ้ามองในเชิงพัฒนาการ บิตคอยน์ก็เหมือนกับอินเทอร์เน็ต ครั้งหนึ่งอินเทอร์เน็ตก็ถูกมองว่าเข้าใจยาก ต้องพิมพ์ http ต้องรู้จัก TCP/IP ต้องตั้ง proxy เอง แต่ปัจจุบันผู้คนใช้งานอินเทอร์เน็ตโดยไม่รู้ว่าเบื้องหลังมีอะไรเลย บิตคอยน์กำลังเดินตามเส้นทางเดียวกัน โปรโตคอลกำลังถอยออกจากสายตา และวันหนึ่งเราจะ “ใช้มัน” โดยไม่ต้องรู้ว่ามันคืออะไร
หากนับจากช่วงเริ่มต้นของอินเทอร์เน็ตในยุค 1990 จนกลายเป็นโครงสร้างหลักของโลกในสองทศวรรษ เส้นเวลาของบิตคอยน์ก็กำลังเดินตามรอยเท้าของอินเทอร์เน็ต และถ้าเราเชื่อว่าวัฏจักรของเทคโนโลยีมีจังหวะของมันเอง เราก็จะรู้ว่า Bitcoin Standard นั้นไม่ใช่เรื่องของอนาคตไกลโพ้น แต่มันเกิดขึ้นแล้ว
-
 @ 9c9d2765:16f8c2c2
2025-05-25 08:26:53
@ 9c9d2765:16f8c2c2
2025-05-25 08:26:53CHAPTER TWENTY EIGHT
“He’s not just surviving,” Helen hissed through clenched teeth, her heels striking the marble floors of her penthouse like war drums. “He’s thriving, and it’s infuriating.”
Mark leaned against the window, watching the evening lights of the city shimmer beneath them. “That transparency stunt he pulled? Genius,” he muttered. “It shut down every accusation we tried to plant before it could sprout.”
Helen turned abruptly. “Then we change the terrain. If he’s building on trust, we flood him with betrayal. We turn his loyalists into doubters.”
Mark raised a brow. “And how do you propose we do that?”
She walked over to the coffee table, picked up a manila envelope, and tossed it onto his lap. It opened with a quiet rustle, revealing photos some staged, others manipulated of James in ambiguous meetings, with headlines drafted in bold red: “JP President Linked to Foreign Espionage?”, “Undisclosed Meetings with Rival Companies.”
“These go live next week,” Helen said coldly. “And if we can’t break his empire from the outside, we’ll corrode it from within.”
Meanwhile, across the city, James stood in the training hall of JP Enterprises, overseeing a leadership seminar. The room brimmed with young professionals, eager minds molded by his vision. He paced slowly, hands behind his back.
“Leadership isn’t about dominance,” he said, his voice calm yet commanding. “It’s about service. True power lies in how many people rise because of you, not how many kneel before you.”
Applause followed, but James’s mind drifted. The storm was coming and he could feel it. The shadows hadn’t retreated; they’d merely been biding their time. But what Helen and Mark underestimated was the strength of what he’d built. This time, he wasn’t alone.
After the seminar, he returned to his office where Rita and Charles were already waiting.
“They’re not backing down,” Rita said, placing a thick fillet on his desk. “Our cybersecurity team intercepted metadata from an anonymous article scheduled to be released next Monday. It traces back to one of Helen’s known shell accounts.”
Charles leaned forward. “They’re targeting your integrity again, James. This time with international implications. If this goes public, it could trigger a full-scale investigation even if the claims are false.”
James took a deep breath. “Then it’s time to activate Project Aegis.”
Rita’s eyes widened. “You mean?”
“Yes,” James affirmed. “Full legal exposure. Every executive, every document, every deal for the last five years. We publish it ourselves before they can twist it.”
Charles nodded slowly, admiration gleaming in his eyes. “You're not just playing defense anymore.”
“No,” James said, his voice resolute. “I’m done playing. It’s time they learn integrity is not a weakness. It’s my greatest strength.”
That same night, Helen and Mark received a notification that sent chills down their spines. Every major news outlet was now broadcasting a preemptive report by JP Enterprises: “A Legacy in the Light JP Enterprises Opens Vaults to Public Scrutiny”. The article was followed by interviews with board members, stakeholders, and long-time employees all affirming James’s character and transparency.
Helen clenched her jaw, watching the screen with cold fury. “He’s rewriting the rules…” she muttered.
“No,” Mark whispered. “He’s building a world where we don’t exist.”
In the quiet of his penthouse office, James stood by the tall glass windows, the city’s nightscape shimmering beneath a sky painted in indigo hues. A cup of untouched coffee sat on the mahogany desk behind him. His reflection merged with the sprawling lights of a man once discarded, now the pillar of a corporate empire.
Despite the outward calm, James’s mind churned like a brewing storm. The recent smear campaign, although crushed by his proactive transparency, had planted seeds of uncertainty in some corners of the public. He knew Helen and Mark were far from surrendering. Their strategy had evolved into psychological warfare planting doubt, sowing division, manipulating perception.
“It’s time to start setting traps of our own,” he murmured under his breath.
He turned from the window as Charles entered the room, holding a tablet.
“It’s worse than we anticipated,” Charles began, concerned with furrowing his brow. “They’ve been funneling money through offshore accounts, paying journalists, bloggers, even some minor influencers to perpetuate false narratives. They’re not just trying to ruin your reputation, they're orchestrating a hostile takeover.”
James exhaled, slowly walking to his desk. “Then we play them at their own game but with honor. I want a full audit of every subsidiary tied to Ray Enterprises and Helen’s private ventures. Any shadow move they’ve made, I want it exposed legally, publicly, and without a hint of impropriety.”
Charles gave a resolute nod. “I’ll get our internal compliance team on it tonight.”
Meanwhile, across town, Helen sat before a marble fireplace in her lavish estate, her fingers tapping impatiently against a crystal glass of wine. Mark sat across from her, scrolling through dozens of negative online articles none of which were about James.
“He flipped the story again,” Mark said bitterly. “People are actually praising him for his transparency. Investors are swarming back. Even media outlets we bribed are retracting their pieces just to avoid a lawsuit.”
Helen’s eyes burned with fury. “Then we escalate. If he wants to play hero, we’ll paint him as a fraud who built an empire on stolen foundations. Everyone has a skeleton buried deep. We just need to find his.”
Back at JP Enterprises, James was meeting with Rita and a trusted cybersecurity analyst, a sharp-eyed woman named Lilian.
“We’ve traced an internal breach,” Lilian reported. “One of the forwarded articles that nearly made it to international outlets was leaked from someone inside our media division.”
Rita frowned. “Tracy.”
James nodded slowly. “She’s the thread connecting Mark and Helen’s plots. But she’s not alone. There’s another… more subtle player behind all this. And I intend to flush them out without alerting the rats.”
The next day, James called a confidential press meeting. With calm confidence, he unveiled The Integrity Initiative, a new transparency program offering unprecedented access to the inner workings of JP Enterprises for all stakeholders.
“We’ve built this company on the belief that truth withstands scrutiny,” he said, his voice echoing through the hall. “We have nothing to hide and for those trying to destroy us with lies, we welcome your eyes. Because when the truth stands tall, shadows disappear.”
The speech went viral within hours. Critics became advocates. Doubters became loyalists. And for Mark and Helen, the walls began to close in faster than they expected.
It had been two days since James’s press conference, and the atmosphere in the city’s business sphere had shifted noticeably. Conversations once filled with doubt and suspicion about JP Enterprises now carried admiration and curiosity. The sudden introduction of The Integrity Initiative had stirred an entirely new level of respect for the company and for James as its helmsman.
-
 @ d360efec:14907b5f
2025-05-13 00:39:56
@ d360efec:14907b5f
2025-05-13 00:39:56🚀📉 #BTC วิเคราะห์ H2! พุ่งชน 105K แล้วเจอแรงขาย... จับตา FVG 100.5K เป็นจุดวัดใจ! 👀📊
จากากรวิเคราะห์ทางเทคนิคสำหรับ #Bitcoin ในกรอบเวลา H2:
สัปดาห์ที่แล้ว #BTC ได้เบรคและพุ่งขึ้นอย่างแข็งแกร่งค่ะ 📈⚡ แต่เมื่อวันจันทร์ที่ผ่านมา ราคาได้ขึ้นไปชนแนวต้านบริเวณ 105,000 ดอลลาร์ แล้วเจอแรงขายย่อตัวลงมาตลอดทั้งวันค่ะ 🧱📉
ตอนนี้ ระดับที่น่าจับตาอย่างยิ่งคือโซน H4 FVG (Fair Value Gap ในกราฟ 4 ชั่วโมง) ที่ 100,500 ดอลลาร์ ค่ะ 🎯 (FVG คือโซนที่ราคาวิ่งผ่านไปเร็วๆ และมักเป็นบริเวณที่ราคามีโอกาสกลับมาทดสอบ/เติมเต็ม)
👇 โซน FVG ที่ 100.5K นี้ ยังคงเป็น Area of Interest ที่น่าสนใจสำหรับมองหาจังหวะ Long เพื่อลุ้นการขึ้นในคลื่นลูกถัดไปค่ะ!
🤔💡 อย่างไรก็ตาม การตัดสินใจเข้า Long หรือเทรดที่บริเวณนี้ ขึ้นอยู่กับว่าราคา แสดงปฏิกิริยาอย่างไรเมื่อมาถึงโซน 100.5K นี้ เพื่อยืนยันสัญญาณสำหรับการเคลื่อนไหวที่จะขึ้นสูงกว่าเดิมค่ะ!
เฝ้าดู Price Action ที่ระดับนี้อย่างใกล้ชิดนะคะ! 📍
BTC #Bitcoin #Crypto #คริปโต #TechnicalAnalysis #Trading #FVG #FairValueGap #PriceAction #MarketAnalysis #ลงทุนคริปโต #วิเคราะห์กราฟ #TradeSetup #ข่าวคริปโต #ตลาดคริปโต


-
 @ 866e0139:6a9334e5
2025-05-23 17:57:24
@ 866e0139:6a9334e5
2025-05-23 17:57:24Autor: Caitlin Johnstone. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Ich hörte einem jungen Autor zu, der eine Idee beschrieb, die ihn so sehr begeisterte, dass er die Nacht zuvor nicht schlafen konnte. Und ich erinnerte mich daran, wie ich mich früher – vor Gaza – über das Schreiben freuen konnte. Dieses Gefühl habe ich seit 2023 nicht mehr gespürt.
Ich beklage mich nicht und bemitleide mich auch nicht selbst, ich stelle einfach fest, wie unglaublich düster und finster die Welt in dieser schrecklichen Zeit geworden ist. Es wäre seltsam und ungesund, wenn ich in den letzten anderthalb Jahren Freude an meiner Arbeit gehabt hätte. Diese Dinge sollen sich nicht gut anfühlen. Nicht, wenn man wirklich hinschaut und ehrlich zu sich selbst ist in dem, was man sieht.
Es war die ganze Zeit über so hässlich und so verstörend. Es gibt eigentlich keinen Weg, all diesen Horror umzudeuten oder irgendwie erträglich zu machen. Alles, was man tun kann, ist, an sich selbst zu arbeiten, um genug inneren Raum zu schaffen, um die schlechten Gefühle zuzulassen und sie ganz durchzufühlen, bis sie sich ausgedrückt haben. Lass die Verzweiflung herein. Die Trauer. Die Wut. Den Schmerz. Lass sie deinen Körper vollständig durchfließen, ohne Widerstand, und steh dann auf und schreibe das nächste Stück.
Das ist es, was Schreiben für mich jetzt ist. Es ist nie etwas, worüber ich mich freue, es zu teilen, oder wofür ich von Inspiration erfüllt bin. Wenn überhaupt, dann fühlt es sich eher so an wie: „Okay, hier bitte, es tut mir schrecklich leid, dass ich euch das zeigen muss, Leute.“ Es ist das Starren in die Dunkelheit, in das Blut, in das Gemetzel, in die gequälten Gesichter – und das Aufschreiben dessen, was ich sehe, Tag für Tag.
Nichts daran ist angenehm oder befriedigend. Es ist einfach das, was man tut, wenn ein Genozid in Echtzeit vor den eigenen Augen stattfindet, mit der Unterstützung der eigenen Gesellschaft. Alles daran ist entsetzlich, und es gibt keinen Weg, das schönzureden – aber man tut, was getan werden muss. So, wie man es täte, wenn es die eigene Familie wäre, die da draußen im Schutt liegt.
Dieser Genozid hat mich für immer verändert. Er hat viele Menschen für immer verändert. Wir werden nie wieder dieselben sein. Die Welt wird nie wieder dieselbe sein. Ganz gleich, was passiert oder wie dieser Albtraum endet – die Dinge werden nie wieder so sein wie zuvor.
Und das sollten sie auch nicht. Der Holocaust von Gaza ist das Ergebnis der Welt, wie sie vor ihm war. Unsere Gesellschaft hat ihn hervorgebracht – und jetzt starrt er uns allen direkt ins Gesicht. Das sind wir. Das ist die Frucht des Baumes, den die westliche Zivilisation bis zu diesem Punkt gepflegt hat.
Jetzt geht es nur noch darum, alles zu tun, was wir können, um den Genozid zu beenden – und sicherzustellen, dass die Welt die richtigen Lehren daraus zieht. Das ist eines der würdigsten Anliegen, denen man sich in diesem Leben widmen kann.
Ich habe noch immer Hoffnung, dass wir eine gesunde Welt haben können. Ich habe noch immer Hoffnung, dass das Schreiben über das, was geschieht, eines Tages wieder Freude bereiten kann. Aber diese Dinge liegen auf der anderen Seite eines langen, schmerzhaften, konfrontierenden Weges, der in den kommenden Jahren vor uns liegt. Es gibt keinen Weg daran vorbei.
Die Welt kann keinen Frieden und kein Glück finden, solange wir uns nicht vollständig damit auseinandergesetzt haben, was wir Gaza angetan haben.
Dieser Text ist die deutsche Übersetzung dieses Substack-Artikels von Caitlin Johnstone.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ d360efec:14907b5f
2025-05-12 04:01:23
@ d360efec:14907b5f
2025-05-12 04:01:23 -
 @ 04c915da:3dfbecc9
2025-05-16 18:06:46
@ 04c915da:3dfbecc9
2025-05-16 18:06:46Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Using stolen bitcoin for the reserve creates a perverse incentive. If governments see bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ a39d19ec:3d88f61e
2025-03-18 17:16:50
@ a39d19ec:3d88f61e
2025-03-18 17:16:50Nun da das deutsche Bundesregime den Ruin Deutschlands beschlossen hat, der sehr wahrscheinlich mit dem Werkzeug des Geld druckens "finanziert" wird, kamen mir so viele Gedanken zur Geldmengenausweitung, dass ich diese für einmal niedergeschrieben habe.
Die Ausweitung der Geldmenge führt aus klassischer wirtschaftlicher Sicht immer zu Preissteigerungen, weil mehr Geld im Umlauf auf eine begrenzte Menge an Gütern trifft. Dies lässt sich in mehreren Schritten analysieren:
1. Quantitätstheorie des Geldes
Die klassische Gleichung der Quantitätstheorie des Geldes lautet:
M • V = P • Y
wobei:
- M die Geldmenge ist,
- V die Umlaufgeschwindigkeit des Geldes,
- P das Preisniveau,
- Y die reale Wirtschaftsleistung (BIP).Wenn M steigt und V sowie Y konstant bleiben, muss P steigen – also Inflation entstehen.
2. Gütermenge bleibt begrenzt
Die Menge an real produzierten Gütern und Dienstleistungen wächst meist nur langsam im Vergleich zur Ausweitung der Geldmenge. Wenn die Geldmenge schneller steigt als die Produktionsgütermenge, führt dies dazu, dass mehr Geld für die gleiche Menge an Waren zur Verfügung steht – die Preise steigen.
3. Erwartungseffekte und Spekulation
Wenn Unternehmen und Haushalte erwarten, dass mehr Geld im Umlauf ist, da eine zentrale Planung es so wollte, können sie steigende Preise antizipieren. Unternehmen erhöhen ihre Preise vorab, und Arbeitnehmer fordern höhere Löhne. Dies kann eine sich selbst verstärkende Spirale auslösen.
4. Internationale Perspektive
Eine erhöhte Geldmenge kann die Währung abwerten, wenn andere Länder ihre Geldpolitik stabil halten. Eine schwächere Währung macht Importe teurer, was wiederum Preissteigerungen antreibt.
5. Kritik an der reinen Geldmengen-Theorie
Der Vollständigkeit halber muss erwähnt werden, dass die meisten modernen Ökonomen im Staatsauftrag argumentieren, dass Inflation nicht nur von der Geldmenge abhängt, sondern auch von der Nachfrage nach Geld (z. B. in einer Wirtschaftskrise). Dennoch zeigt die historische Erfahrung, dass eine unkontrollierte Geldmengenausweitung langfristig immer zu Preissteigerungen führt, wie etwa in der Hyperinflation der Weimarer Republik oder in Simbabwe.
-
 @ 8d34bd24:414be32b
2025-05-25 06:29:21
@ 8d34bd24:414be32b
2025-05-25 06:29:21It seems like most Christians today have lost their reverence and awe of God. We’ve attributed God’s awesome creation by the word of His mouth to random chance and a Big Bang. We’ve attributed the many layers of sediment to millions and billions of years of time instead of God’s judgment of evil. We’ve emphasized His love and mercy to the point that we’ve forgotten about His holiness and righteous wrath. We’ve brought God down to our level and made Him either our “buddy” or made Him our magic genie servant, who is just there to answer our every want and whim.
The God of the Bible is a holy and awesome God who should be both loved and feared.
The fear of the Lord is the beginning of knowledge;\ Fools despise wisdom and instruction. (Proverbs 1:7)
The God of the Bible is the Lord of Lords and King of Kings who “… upholds all things by the word of His power. …” (Hebrews 1:3). Yes, God loves us as sons. Yes, God is merciful. Yes, through Jesus we have the blessed opportunity to approach God directly. None of that means we get to treat God like just another friend. We are to approach God with fear and trembling and worship Him in reverence and awe.
Worship the Lord with reverence And rejoice with trembling. (Psalm 2:11)
Part of the problem is that our culture just doesn’t show reverence to authority. It focuses on self and freedom. The whole thought of reverence for authority is incomprehensible for many. Look at this Psalm of worship:
The Lord reigns, let the peoples tremble;\ He is enthroned above the cherubim, let the earth shake!\ The Lord is great in Zion,\ And He is exalted above all the peoples.\ Let them praise Your great and awesome name;\ Holy is He. (Psalm 99:1-3)
This is the way we should view God and the proper attitude for approaching God.
Another issue is that we don’t study what God has done in the past. In the Old Testament, God commanded the Israelites to setup monuments of remembrance and to teach their kids all of the great things God had done for them. When they failed to do so, Israel drifted astray.
You shall teach them to your sons, talking of them when you sit in your house and when you walk along the road and when you lie down and when you rise up. (Deuteronomy 11:19)
God has given us the Bible, His word, so that we can know Him, know His character, and know His great deeds. When we fail to be in His word daily, we can forget (or not even know) the greatness of our God.
Establish Your word to Your servant,\ As that which produces reverence for You. (Psalm 119:38)
Do you love God’s word like this? Do you hunger for God’s word? Do you seek to know everything about God that you can know? When we love someone or something, we want to know everything about it.
Princes persecute me without cause,\ But my heart stands in awe of Your words.\ **I rejoice at Your word,\ As one who finds great spoil. \ (Psalm 119:161-162) {emphasis mine}
In addition to what we can learn about God in the Bible, we also need to remember what God has done in our own lives. We need to dwell on what God has done for us. We can just try to remember. Even better (I’ll admit this is a weakness for me), write down answered prayers, blessings, and other things God has done for you. My son has been writing down one blessing every day for over a year. What an example he is!
After we have thought about what God has done for us and those we care about, we should praise Him for His great works.
Shout joyfully to God, all the earth;\ Sing the glory of His name;\ Make His praise glorious.\ Say to God, “How awesome are Your works!\ Because of the greatness of Your power \ Your enemies will give feigned obedience to You.\ All the earth will worship You,\ And will sing praises to You;\ They will sing praises to Your name.” Selah.\ **Come and see the works of God,\ Who is awesome in His deeds toward the sons of men. \ (Psalm 66:1-5) {emphasis mine}
There is nothing we can do to earn salvation from God, but we should be in awe of what He has done for us leading to submission and obedience in gratitude.
Therefore, since we receive a kingdom which cannot be shaken, let us show gratitude, by which we may offer to God an acceptable service with reverence and awe; for our God is a consuming fire. (Hebrews 12:28-29) {emphasis mine}
Are you thankful for your blessings or resentful for what you don’t have? Do you worship God or take things He has provided for granted? Do you tell the world the awesome things God has done for you or do you stay silent? Do you claim to be a Christian, but live a life no different than those around you?
Then the Lord said,
“Because this people draw near with their words\ And honor Me with their lip service,\ But they remove their hearts far from Me,\ And their reverence for Me consists of tradition learned by rote, (Isaiah 29:13)
I hope this passage does not describe your relation ship with our awesome God. He deserves so much more. Instead we should be zealous to praise God and share His goodness with those around us.
Who is there to harm you if you prove zealous for what is good? But even if you should suffer for the sake of righteousness, you are blessed. And do not fear their intimidation, and do not be troubled, but sanctify Christ as Lord in your hearts, always being ready to make a defense to everyone who asks you to give an account for the hope that is in you, yet with gentleness and reverence; (1 Peter 3:13-15) {emphasis mine}
Did you know that you can even show reverence by your every day work?
By faith Noah, being warned by God about things not yet seen, in reverence prepared an ark for the salvation of his household, by which he condemned the world, and became an heir of the righteousness which is according to faith. (Hebrews 11:7) {emphasis mine}
When Noah stepped out in faith and obedience to God and built the ark as God commanded, despite the fact that the people around him probably thought he was crazy building a boat on dry ground that had never flooded, his work was a kind of reverence to God. Are there areas in your life where you can obey God in reverence to His awesomeness? Do you realize that quality work in obedience to God can be a form of worship?
Just going above and beyond in your job can be a form of worship of God if you are working extra hard to honor Him. Obedience is another form of worship and reverence.
Then Zerubbabel the son of Shealtiel, and Joshua the son of Jehozadak, the high priest, with all the remnant of the people, obeyed the voice of the Lord their God and the words of Haggai the prophet, as the Lord their God had sent him. And the people showed reverence for the Lord. (Haggai 1:12) {emphasis mine}
Too many people have put the word of men (especially scientists) above the word of God and have tried to change the clear meaning of the Bible. I used to think it strange how the Bible goes through the days of creation and ends each day with “and there was evening and there was morning, the xth day.” Since a day has an evening and a morning, that seemed redundant. Why did God speak in this manner? God knew that a day would come when many scientist would try to disprove God and would claim that these days were not 24 hour days, but long ages. When a writer is trying to convey long ages, the writer does not mention evening/morning and doesn’t count the days.1
When we no longer see God as speaking the universe and everything in it into existence, we tend to not see God as an awesome God. We don’t see His power. We don’t see His knowledge. We don’t see His goodness. We also don’t see His authority. Why do we have to obey God? Because He created us and because He upholds us. Without Him we would not exist. Our creator has the authority to command His creation. When we compromise in this area, we lose our submission, our awe, and our reverence. (For more on the subject see my series.) When we believe His great works, especially those spoken of in Genesis 1-11 and in Exodus, we can’t help but be in awe of our God.
For the word of the Lord is upright,\ And all His work is done in faithfulness.\ He loves righteousness and justice;\ The earth is full of the lovingkindness of the Lord.\ By the word of the Lord the heavens were made,\ And by the breath of His mouth all their host.\ He gathers the waters of the sea together as a heap;\ He lays up the deeps in storehouses.\ **Let all the earth fear the Lord;\ Let all the inhabitants of the world stand in awe of Him. \ (Psalm 33:4-8) {emphasis mine}
Remembering God’s great works, we can’t help but worship in awe and reverence.
By awesome deeds You answer us in righteousness, O God of our salvation,\ *You who are the trust of all the ends of the earth* and of the farthest sea;\ Who establishes the mountains by His strength,\ Being girded with might;\ Who stills the roaring of the seas,\ The roaring of their waves,\ And the tumult of the peoples.\ They who dwell in the ends of the earth stand in awe of Your signs;\ You make the dawn and the sunset shout for joy. \ (Psalm 65:5-8) {emphasis mine}
If we truly do have awe and reverence for our God, we should be emboldened to tell those around us of His great works.
I will tell of Your name to my brethren;\ In the midst of the assembly I will praise You.\ You who fear the Lord, praise Him;\ All you descendants of Jacob, glorify Him,\ And stand in awe of Him, all you descendants of Israel. \ (Psalm 22:22-23) {emphasis mine}
May God grant you the wisdom to see His awesomeness and to trust Him, serve Him, obey Him, and worship Him as He so rightly deserves. May you always have a right view of God and a hunger for His word and a personal relationship with Him. To God be the Glory!
Trust Jesus
FYI, these are a few more passages on the subject that are helpful, but didn’t fit in the flow of my post.
Great is the Lord, and highly to be praised,\ And His greatness is unsearchable.\ One generation shall praise Your works to another,\ And shall declare Your mighty acts.\ On the glorious splendor of Your majesty\ And on Your wonderful works, I will meditate.\ Men shall speak of the power of Your awesome acts,\ And I will tell of Your greatness. (Psalm 145:3-6)
The boastful shall not stand before Your eyes;\ You hate all who do iniquity.\ You destroy those who speak falsehood;\ The Lord abhors the man of bloodshed and deceit.\ But as for me, by Your abundant lovingkindness I will enter Your house,\ At Your holy temple I will bow in reverence for You. (Psalm 5:5-7) {emphasis mine}
If you do not listen, and if you do not take it to heart to give honor to My name,” says the Lord of hosts, “then I will send the curse upon you and I will curse your blessings; and indeed, I have cursed them already, because you are not taking it to heart. Behold, I am going to rebuke your offspring, and I will spread refuse on your faces, the refuse of your feasts; and you will be taken away with it. Then you will know that I have sent this commandment to you, that My covenant may continue with Levi,” says the Lord of hosts. “My covenant with him was one of life and peace, and I gave them to him as an object of reverence; so he revered Me and stood in awe of My name. (Malachi 2:2-5) {emphasis mine}
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 9c9d2765:16f8c2c2
2025-05-25 08:14:32
@ 9c9d2765:16f8c2c2
2025-05-25 08:14:32CHAPTER TWENTY SEVEN “We’re finished,” she snapped, pacing furiously. “They’ve locked every door. We’ve been blacklisted by every reputable firm in the city. No one's taking our calls, and now the tax authorities are sniffing around!”
Mark stood slowly, still holding the glass. “It’s all because of him,” he growled. “James. That street rat turned king. He’s poisoned the whole industry against us.”
Helen scoffed. “He didn’t poison it. He conquered it. You and I? We underestimated him. We saw rags and never imagined the gold beneath.”
There was a moment of raw, uncomfortable silence.
“And now,” she added bitterly, “he owns not just the Ray company but the story. The people adore him. Every misstep we make adds to his legend.”
Mark turned away, the fury in his chest simmering just below the surface. “Then maybe it’s time we stop playing by his rules.”
Helen raised an eyebrow. “What are you thinking?”
“Something permanent,” he said coldly. “Something that’ll make the city question his legacy. We won’t touch him directly. But we’ll dismantle everything around him his alliances, his investors, his trust.”
Meanwhile, at JP Enterprises, James was meeting with his board members. The mood was triumphant. Contracts were flowing in from across the nation. Investors from overseas were lining up to collaborate. JP Enterprises was no longer a local giant, it was becoming a global force.
As the board meeting wrapped up, Charles approached James with a discreet file.
“We’ve uncovered something,” he said in a hushed tone. “Helen and Mark have begun contacting shell companies. They’re orchestrating something through offshore accounts. It’s not clear yet, but they’re moving funds and people.”
James took the file, flipping through the pages with a calm intensity. “They never learn,” he murmured. “Desperation is a dangerous motivator.”
Charles nodded. “Shall we alert the authorities?”
James paused. “Not yet. Let them think they’re getting away with it. Let them build the stage. And when the curtains rise, we’ll pull the spotlight on them ourselves.”
Outside, the sky turned amber as dusk crept over the horizon. Somewhere in the city, Mark and Helen were plotting their next move. But in the heart of JP Enterprises, James was already five steps ahead.
The night veiled the city in a silvery calm, but within the walls of an abandoned warehouse at the edge of town, shadows danced beneath flickering fluorescent lights. Mark and Helen stood amidst crates of outdated office furniture and rusted metal, far removed from the lavish boardrooms they once commanded. Their pride, now fragments, echoed in every creak of the floor beneath them.
“We’ve traced every name that still owes us favors,” Mark said, unfolding a large sheet of paper across a makeshift table. “This is our web. Media contacts. Shell consultants. A few digital mercenaries.”
Helen leaned over the table, eyes scanning the diagram. “It’s not about hitting him,” she whispered. “It’s about bleeding his legacy. Bit by bit. We drown him in whispers, not weapons.”
Their plan was insidious smear campaigns seeded in anonymous blogs, fabricated audits from paid ‘inspectors,’ leaks of doctored company records, and the reawakening of James’s past, even if the ghosts had already been proven false. They would question every victory he had, casting shadows over every triumph. If they couldn’t win, they would ruin the game.
Meanwhile, back at JP Enterprises, James sat in his office high above the city. The glass walls gave him a breathtaking view, but his gaze was introspective. His mind wandered through recent events the betrayal, the accusations, the painful resurgence of a forgotten past. But what stood out most was not the malice of others. It was how he had endured.
Charles entered the office, a slight knock preceding him. “We’ve secured the last two tech firms you were eyeing. Their CEOs are prepared to sign exclusive partnerships. Also, the board wants to recognize you officially as Global CEO during next month’s summit.”
James smiled faintly, though his eyes retained a solemn hue. “Good. But there’s something more important.” He turned his laptop around, displaying a series of anonymous online threads riddled with false claims and slander.
“They’ve begun,” he said softly. “Helen and Mark are orchestrating a campaign to rot our foundation from the inside out.”
Charles's expression darkened. “Should I initiate a counter-sweep?”
James shook his head. “No. We don’t fight shadows with swords. We fight them with light.” He paused, then added, “I want full transparency reports across every department. I want our investors to see our books before they ask. I want our work to speak so loudly, their lies get drowned out.”
In a conference the following morning, James stood before hundreds of stakeholders and partners, unveiling a revolutionary corporate transparency portal. Real-time audits, project status updates, and salary distributions were now accessible to all registered partners. The press called it “the death of corporate secrecy.”
While Mark and Helen were weaving illusions, James was showcasing reality.
Yet in the shadows, Helen grew more frustrated.
“He’s not cracking!” she shouted, hurling a tablet against the floor. “How is he still standing?”
Mark sat, quiet for once, rubbing his temples. “Because he’s not the man we knew. He’s not the beggar we mocked. He’s become… untouchable.”
Helen turned, her eyes blazing. “Then we don’t touch him. We find someone he cares about. We make him feel vulnerable again.”
Mark didn’t speak, but the silence between them felt like a pact being sealed.
Back at JP Enterprises, James met with Rita. Her sharpness and integrity had restored much of the company’s cultural fabric. He trusted her, more than most. And as they walked the office floors together, they discussed not just projects, but the future that would soon test every bond, every alliance.
-
 @ 2b998b04:86727e47
2025-05-25 03:28:59
@ 2b998b04:86727e47
2025-05-25 03:28:59Turning 60
Ten years ago, I turned 50 with a vague sense that something was off.
I was building things, but they didn’t feel grounded.\ I was "in tech," but tech felt like a treadmill—just faster, sleeker tools chasing the same hollow outcomes.\ I knew about Bitcoin, but I dismissed it. I thought it was just “tech for tech’s sake.”
Less than a year later, I fell down the rabbit hole.
It didn’t happen all at once. At first it was curiosity. Then dissonance. Then conviction.
Somewhere in that process, I realized Bitcoin wasn’t just financial—it was philosophical. It was moral. It was real. And it held up a mirror to a life I had built on momentum more than mission.
So I started pruning.
I left Web3.\ I pulled back from projects that ran on hype instead of honesty.\ I repented—for chasing relevance instead of righteousness.\ And I began stacking—not just sats, but new habits. New thinking. New rhythms of faith, work, and rest.
Now at 60, I’m not where I thought I’d be.
But I’m more myself than I’ve ever been.\ More convicted.\ More rooted.\ More ready.
Not to start over—but to build again, from the foundation up.
If you're in that middle place—between chapters, between convictions, between certainty and surrender—you're not alone.
🟠 I’m still here. Still building. Still listening.
Zap if this resonates, or send your story. I’d love to hear it.
[*Zap *](https://tinyurl.com/yuyu2b9t)
-
 @ 0d97beae:c5274a14
2025-01-11 16:52:08
@ 0d97beae:c5274a14
2025-01-11 16:52:08This article hopes to complement the article by Lyn Alden on YouTube: https://www.youtube.com/watch?v=jk_HWmmwiAs
The reason why we have broken money
Before the invention of key technologies such as the printing press and electronic communications, even such as those as early as morse code transmitters, gold had won the competition for best medium of money around the world.
In fact, it was not just gold by itself that became money, rulers and world leaders developed coins in order to help the economy grow. Gold nuggets were not as easy to transact with as coins with specific imprints and denominated sizes.
However, these modern technologies created massive efficiencies that allowed us to communicate and perform services more efficiently and much faster, yet the medium of money could not benefit from these advancements. Gold was heavy, slow and expensive to move globally, even though requesting and performing services globally did not have this limitation anymore.
Banks took initiative and created derivatives of gold: paper and electronic money; these new currencies allowed the economy to continue to grow and evolve, but it was not without its dark side. Today, no currency is denominated in gold at all, money is backed by nothing and its inherent value, the paper it is printed on, is worthless too.
Banks and governments eventually transitioned from a money derivative to a system of debt that could be co-opted and controlled for political and personal reasons. Our money today is broken and is the cause of more expensive, poorer quality goods in the economy, a larger and ever growing wealth gap, and many of the follow-on problems that have come with it.
Bitcoin overcomes the "transfer of hard money" problem
Just like gold coins were created by man, Bitcoin too is a technology created by man. Bitcoin, however is a much more profound invention, possibly more of a discovery than an invention in fact. Bitcoin has proven to be unbreakable, incorruptible and has upheld its ability to keep its units scarce, inalienable and counterfeit proof through the nature of its own design.
Since Bitcoin is a digital technology, it can be transferred across international borders almost as quickly as information itself. It therefore severely reduces the need for a derivative to be used to represent money to facilitate digital trade. This means that as the currency we use today continues to fare poorly for many people, bitcoin will continue to stand out as hard money, that just so happens to work as well, functionally, along side it.
Bitcoin will also always be available to anyone who wishes to earn it directly; even China is unable to restrict its citizens from accessing it. The dollar has traditionally become the currency for people who discover that their local currency is unsustainable. Even when the dollar has become illegal to use, it is simply used privately and unofficially. However, because bitcoin does not require you to trade it at a bank in order to use it across borders and across the web, Bitcoin will continue to be a viable escape hatch until we one day hit some critical mass where the world has simply adopted Bitcoin globally and everyone else must adopt it to survive.
Bitcoin has not yet proven that it can support the world at scale. However it can only be tested through real adoption, and just as gold coins were developed to help gold scale, tools will be developed to help overcome problems as they arise; ideally without the need for another derivative, but if necessary, hopefully with one that is more neutral and less corruptible than the derivatives used to represent gold.
Bitcoin blurs the line between commodity and technology
Bitcoin is a technology, it is a tool that requires human involvement to function, however it surprisingly does not allow for any concentration of power. Anyone can help to facilitate Bitcoin's operations, but no one can take control of its behaviour, its reach, or its prioritisation, as it operates autonomously based on a pre-determined, neutral set of rules.
At the same time, its built-in incentive mechanism ensures that people do not have to operate bitcoin out of the good of their heart. Even though the system cannot be co-opted holistically, It will not stop operating while there are people motivated to trade their time and resources to keep it running and earn from others' transaction fees. Although it requires humans to operate it, it remains both neutral and sustainable.
Never before have we developed or discovered a technology that could not be co-opted and used by one person or faction against another. Due to this nature, Bitcoin's units are often described as a commodity; they cannot be usurped or virtually cloned, and they cannot be affected by political biases.
The dangers of derivatives
A derivative is something created, designed or developed to represent another thing in order to solve a particular complication or problem. For example, paper and electronic money was once a derivative of gold.
In the case of Bitcoin, if you cannot link your units of bitcoin to an "address" that you personally hold a cryptographically secure key to, then you very likely have a derivative of bitcoin, not bitcoin itself. If you buy bitcoin on an online exchange and do not withdraw the bitcoin to a wallet that you control, then you legally own an electronic derivative of bitcoin.
Bitcoin is a new technology. It will have a learning curve and it will take time for humanity to learn how to comprehend, authenticate and take control of bitcoin collectively. Having said that, many people all over the world are already using and relying on Bitcoin natively. For many, it will require for people to find the need or a desire for a neutral money like bitcoin, and to have been burned by derivatives of it, before they start to understand the difference between the two. Eventually, it will become an essential part of what we regard as common sense.
Learn for yourself
If you wish to learn more about how to handle bitcoin and avoid derivatives, you can start by searching online for tutorials about "Bitcoin self custody".
There are many options available, some more practical for you, and some more practical for others. Don't spend too much time trying to find the perfect solution; practice and learn. You may make mistakes along the way, so be careful not to experiment with large amounts of your bitcoin as you explore new ideas and technologies along the way. This is similar to learning anything, like riding a bicycle; you are sure to fall a few times, scuff the frame, so don't buy a high performance racing bike while you're still learning to balance.
-
 @ 57d1a264:69f1fee1
2025-05-25 06:26:42
@ 57d1a264:69f1fee1
2025-05-25 06:26:42I dare to claim that the big factor is the absence of an infinite feed design.
Modern social media landscape sucks for a myriad of reasons, but oh boy does the infinite feed take the crapcake. It's not just bad on it's own, it's emblematic of most, if not all other ways social media have deteriorated into an enshitification spiral. Let's see at just three things I hate about it the most.
1) It's addictive: In the race for your attention, every addictive design element helps. But infinite feed is addictive almost by default. Users are expected to pull the figurative lever until they hit a jackpot. Just one more reel, then I'll go to sleep.
2) Autonomy? What's that? You are not the one driving your experience. No. You are just a passenger passively absorbing what the feed feeds you.
3) Echo chambers. The algorithm might be more to blame here, but the infinite feed and it's super-limited exploration options sure don't help. Your feed only goes two ways - into the past and into the comfortable.
And I could go on, and on...
The point it, if the goal of every big tech company is to have us mindlessly and helplessly consume their products, without agency and opposition (and it is $$$), then the infinite feed gets them half-way there.
Let's get rid of it. For the sake of humanity.
Aphantasia [^1]
Version: 1.0.2 AlphaWhat is Aphantasia?
I like to call it a social network for graph enthusiasts. It's a place where your thoughts live in time and space, interconnected with others and explorable in a graph view.
The code is open-source and you can take a look at it on GitHub. There you can find more information about contributions, API usage and other details related to the software.
There is also an accompanying youtube channel.
https://www.youtube.com/watch?v=JeLOt-45rJM
[^1]: Aphantasia the software is named after aphantasia the condition - see Wikipedia for more information.
https://stacker.news/items/988754
-
 @ 37fe9853:bcd1b039
2025-01-11 15:04:40
@ 37fe9853:bcd1b039
2025-01-11 15:04:40yoyoaa
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ d360efec:14907b5f
2025-05-12 01:34:24
@ d360efec:14907b5f
2025-05-12 01:34:24สวัสดีค่ะเพื่อนๆ นักเทรดที่น่ารักทุกคน! 💕 Lina Engword กลับมาพร้อมกับการวิเคราะห์ BTCUSDT.P แบบเจาะลึกเพื่อเตรียมพร้อมสำหรับเทรดวันนี้ค่ะ! 🚀
วันนี้ 12 พฤษภาคม 2568 เวลา 08.15น. ราคา BTCUSDT.P อยู่ที่ 104,642.8 USDT ค่ะ โดยมี Previous Weekly High (PWH) อยู่ที่ 104,967.8 Previous Weekly Low (PWL) ที่ 93,338 ค่ะ
✨ ภาพรวมตลาดวันนี้ ✨
จากการวิเคราะห์ด้วยเครื่องมือคู่ใจของเรา ทั้ง SMC/ICT (Demand/Supply Zone, Order Block, Liquidity), EMA 50/200, Trend Strength, Money Flow, Chart/Price Pattern, Premium/Discount Zone, Trend line, Fibonacci, Elliott Wave และ Dow Theory ใน Timeframe ตั้งแต่ 15m ไปจนถึง Week! 📊 เราพบว่าภาพใหญ่ของ BTCUSDT.P ยังคงอยู่ในแนวโน้มขาขึ้นที่แข็งแกร่งมากๆ ค่ะ 👍 โดยเฉพาะใน Timeframe Day และ Week ที่สัญญาณทุกอย่างสนับสนุนทิศทางขาขึ้นอย่างชัดเจน Money Flow ยังไหลเข้าอย่างต่อเนื่อง และเราเห็นโครงสร้างตลาดแบบ Dow Theory ที่ยก High ยก Low ขึ้นไปเรื่อยๆ ค่ะ
อย่างไรก็ตาม... ใน Timeframe สั้นๆ อย่าง 15m และ 1H เริ่มเห็นสัญญาณของการชะลอตัวและการพักฐานบ้างแล้วค่ะ 📉 อาจมีการสร้าง Buyside และ Sellside Liquidity รอให้ราคาไปกวาดก่อนที่จะเลือกทางใดทางหนึ่ง ซึ่งเป็นเรื่องปกติของการเดินทางของ Smart Money ค่ะ
⚡ เปรียบเทียบแนวโน้มแต่ละ Timeframe ⚡
🪙 แนวโน้มตรงกัน Timeframe 4H, Day, Week ส่วนใหญ่ชี้ไปทาง "ขาขึ้น" ค่ะ ทุกเครื่องมือสนับสนุนแนวโน้มนี้อย่างแข็งแกร่ง 💪 เป้าหมายต่อไปคือการไปทดสอบ PWH และ High เดิม เพื่อสร้าง All-Time High ใหม่ค่ะ! 🪙 แนวโน้มต่างกัน Timeframe 15m, 1H ยังค่อนข้าง "Sideways" หรือ "Sideways Down เล็กน้อย" ค่ะ มีการบีบตัวของราคาและอาจมีการพักฐานสั้นๆ ซึ่งเป็นโอกาสในการหาจังหวะเข้า Long ที่ราคาดีขึ้นค่ะ
💡 วิธีคิดแบบ Market Slayer 💡
เมื่อแนวโน้มใหญ่เป็นขาขึ้นที่แข็งแกร่ง เราจะเน้นหาจังหวะเข้า Long เป็นหลักค่ะ การย่อตัวลงมาในระยะสั้นคือโอกาสของเราในการเก็บของ! 🛍️ เราจะใช้หลักการ SMC/ICT หาโซน Demand หรือ Order Block ที่ Smart Money อาจจะเข้ามาดันราคาขึ้น และรอสัญญาณ Price Action ยืนยันการกลับตัวค่ะ
สรุปแนวโน้มวันนี้:
🪙 ระยะสั้น: Sideways to Sideways Down (โอกาส 55%) ↔️↘️ 🪙 ระยะกลาง: ขาขึ้น (โอกาส 70%) ↗️ 🪙 ระยะยาว: ขาขึ้น (โอกาส 85%) 🚀 🪙 วันนี้: มีโอกาสย่อตัวเล็กน้อยก่อนจะมีแรงซื้อกลับเข้ามาเพื่อไปทดสอบ PWH (โอกาส Sideways Down เล็กน้อย สลับกับ Sideways Up: 60%) 🎢
🗓️ Daily Trade Setup ประจำวันนี้ 🗓️
นี่คือตัวอย่าง Setup ที่ Lina เตรียมไว้ให้พิจารณาค่ะ (เน้นย้ำว่าเป็นเพียงแนวทาง ไม่ใช่คำแนะนำลงทุนนะคะ)
1️⃣ ตัวอย่างที่ 1: รอรับที่โซน Demand (ปลอดภัย, รอยืนยัน)
🪙 Enter: รอราคาย่อตัวลงมาในโซน Demand Zone หรือ Bullish Order Block ที่น่าสนใจใน TF 1H/4H (ดูจากกราฟประกอบนะคะ) และเกิดสัญญาณ Bullish Price Action ที่ชัดเจน เช่น แท่งเทียนกลืนกิน (Engulfing) หรือ Hammer 🪙 TP: บริเวณ PWH 104,967.8 หรือ Buyside Liquidity ถัดไป 🎯 🪙 SL: ใต้ Low ที่เกิดก่อนสัญญาณกลับตัวเล็กน้อย หรือใต้ Demand Zone ที่เข้า 🛡️ 🪙 RRR: ประมาณ 1:2.5 ขึ้นไป ✨ 🪙 อธิบาย: Setup นี้เราจะใจเย็นๆ รอให้ราคาลงมาในโซนที่มีโอกาสเจอแรงซื้อเยอะๆ ตามหลัก SMC/ICT แล้วค่อยเข้า เพื่อให้ได้ราคาที่ดีและความเสี่ยงต่ำค่ะ ต้องรอสัญญาณ Price Action ยืนยันก่อนนะคะ ✍️
2️⃣ ตัวอย่างที่ 2: Follow Breakout (สายบู๊, รับความเสี่ยงได้)
🪙 Enter: เข้า Long ทันทีเมื่อราคาสามารถ Breakout เหนือ High ล่าสุดใน TF 15m หรือ 1H พร้อม Volume ที่เพิ่มขึ้นอย่างมีนัยสำคัญ 🔥 🪙 TP: บริเวณ PWH 104,967.8 หรือ Buyside Liquidity ถัดไป 🚀 🪙 SL: ใต้ High ก่อนหน้าที่ถูก Breakout เล็กน้อย 🚧 🪙 RRR: ประมาณ 1:3 ขึ้นไป ✨ 🪙 อธิบาย: Setup นี้เหมาะกับคนที่อยากเข้าไวเมื่อเห็นโมเมนตัมแรงๆ ค่ะ เราจะเข้าเมื่อราคา Breakout แนวต้านระยะสั้นพร้อม Volume เป็นสัญญาณว่าแรงซื้อกำลังมาค่ะ เข้าได้เลยด้วยการตั้ง Limit Order หรือ Market Order เมื่อเห็นการ Breakout ที่ชัดเจนค่ะ 💨
3️⃣ ตัวอย่างที่ 3: พิจารณา Short สั้นๆ ในโซน Premium (สวนเทรนด์หลัก, ความเสี่ยงสูง)
🪙 Enter: หากราคาขึ้นไปในโซน Premium ใน TF 15m หรือ 1H และเกิดสัญญาณ Bearish Price Action ที่ชัดเจน เช่น แท่งเทียน Shooting Star หรือ Bearish Engulfing บริเวณ Supply Zone หรือ Bearish Order Block 🐻 🪙 TP: พิจารณาแนวรับถัดไป หรือ Sellside Liquidity ใน TF เดียวกัน 🎯 🪙 SL: เหนือ High ของสัญญาณ Bearish Price Action เล็กน้อย 💀 🪙 RRR: ประมาณ 1:1.5 ขึ้นไป (เน้นย้ำว่าเป็นการเทรดสวนเทรนด์หลัก ควรใช้ RRR ต่ำและบริหารขนาด Lot อย่างเข้มงวด!) 🪙 อธิบาย: Setup นี้สำหรับคนที่เห็นโอกาสในการทำกำไรจากการย่อตัวระยะสั้นค่ะ เราจะเข้า Short เมื่อเห็นสัญญาณว่าราคาอาจจะมีการพักฐานในโซนที่ถือว่า "แพง" ในกรอบสั้นๆ ค่ะ ต้องตั้ง Stop Loss ใกล้มากๆ และจับตาดูใกล้ชิดนะคะ 🚨
⚠️ Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัวของ Lina เท่านั้น ไม่ถือเป็นคำแนะนำในการลงทุนนะคะ การลงทุนมีความเสี่ยง ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบค่ะ 🙏
ขอให้ทุกท่านโชคดีกับการเทรดในวันนี้ค่ะ! มีคำถามอะไรเพิ่มเติม ถามมาได้เลยนะคะ ยินดีเสมอค่ะ! 😊
Bitcoin #BTCUSDT #Crypto #Trading #TechnicalAnalysis #SMC #ICT #MarketSlayer #TradeSetup #คริปโต #เทรดคริปโต #วิเคราะห์กราฟ #LinaEngword 😉



-
 @ cefb08d1:f419beff
2025-05-25 07:39:53
@ cefb08d1:f419beff
2025-05-25 07:39:53https://stacker.news/items/988759
-
 @ 62033ff8:e4471203
2025-01-11 15:00:24
@ 62033ff8:e4471203
2025-01-11 15:00:24收录的内容中 kind=1的部分,实话说 质量不高。 所以我增加了kind=30023 长文的article,但是更新的太少,多个relays 的服务器也没有多少长文。
所有搜索nostr如果需要产生价值,需要有高质量的文章和新闻。 而且现在有很多机器人的文章充满着浪费空间的作用,其他作用都用不上。
https://www.duozhutuan.com 目前放的是给搜索引擎提供搜索的原材料。没有做UI给人类浏览。所以看上去是粗糙的。 我并没有打算去做一个发microblog的 web客户端,那类的客户端太多了。
我觉得nostr社区需要解决的还是应用。如果仅仅是microblog 感觉有点够呛
幸运的是npub.pro 建站这样的,我觉得有点意思。
yakihonne 智能widget 也有意思
我做的TaskQ5 我自己在用了。分布式的任务系统,也挺好的。
-
 @ 21810ca8:f2e8341e
2025-05-25 05:02:33
@ 21810ca8:f2e8341e
2025-05-25 05:02:33If so, please comment. So I can see if Nostr works for me.
-
 @ 2b998b04:86727e47
2025-05-25 03:19:19
@ 2b998b04:86727e47
2025-05-25 03:19:19n an inflationary system, the goal is often just to keep up.
With prices always rising, most of us are stuck in a race:\ Earn more to afford more.\ Spend before your money loses value.\ Monetize everything just to stay ahead of the curve.
Work becomes reactive.\ You hustle to outrun rising costs.\ You take on projects you don’t believe in just to make next month’s bills.\ Money decays. So you move faster, invest riskier, and burn out quicker.
But what happens when the curve flips?
A deflationary economy—like the one Bitcoin makes possible—rewards stillness, reflection, and intentionality.
Time favors the saver, not the spender.\ Money gains purchasing power.\ You’re no longer punished for patience.
You don’t have to convert your energy into cash before it loses value.\ You don’t have to be always on.\ You can actually afford to wait for the right work.
And when you do work—it means more.
💡 The “bullshit jobs” David Graeber wrote about start to disappear.\ There’s no need to look busy just to justify your existence.\ There’s no reward for parasitic middle layers.\ Instead, value flows to real craft, real care, and real proof of work—philosophically and literally.
So what does a job look like in that world?
— A farmer building soil instead of chasing subsidies.\ — An engineer optimizing for simplicity instead of speed.\ — A craftsman making one perfect table instead of ten cheap ones.\ — A writer telling the truth without clickbait.\ — A builder who says no more than they say yes.
You choose work that endures—not because it pays instantly, but because it’s worth doing.
The deflationary future isn’t a fantasy.\ It’s a recalibration.
It’s not about working less.\ It’s about working better.
That’s what Bitcoin taught me.\ That’s what I’m trying to live now.
🟠 If you’re trying to align your work with these values, I’d love to connect.\ Zap this post, reply with your story, or follow along as I build—without permission, but with conviction.\ [https://tinyurl.com/yuyu2b9t](https://tinyurl.com/yuyu2b9t)
-
 @ eb0157af:77ab6c55
2025-05-25 04:48:11
@ eb0157af:77ab6c55
2025-05-25 04:48:11Michigan lawmakers are unveiling a comprehensive strategy to regulate Bitcoin and cryptocurrencies.
On May 21, Republican Representative Bill Schuette introduced House Bill 4510, a proposal to amend the Michigan Public Employee Retirement System Investment Act. The legislation would allow the state treasurer, currently Rachael Eubanks, to diversify the state’s investments by including cryptocurrencies with an average market capitalization of over $250 million in the past calendar year.
Under current criteria, Bitcoin (BTC) and Ether (ETH) are the only cryptocurrencies that meet these selection standards. The proposal specifies that any investment in digital assets must be made through exchange-traded products (spot ETFs) issued by registered investment companies.
Anti-CBDC legislation
Republican Representative Bryan Posthumus is leading the bipartisan initiative behind the second bill, HB 4511, which establishes protections for cryptocurrency holders. The proposal prohibits Michigan from implementing crypto bans or imposing licensing requirements on digital asset holders.
Another key aspect of the legislation is a ban on state officials from supporting or promoting a potential federal central bank digital currency (CBDC). The definition includes the issuance of memorandums or official statements endorsing CBDC proposals related to testing, adoption, or implementation.
Mining and redevelopment of abandoned sites
The third bill, HB 4512, is a proposal led by Democratic Representative Mike McFall for a bipartisan group. This initiative would establish a Bitcoin mining program allowing operators to use abandoned oil and natural gas sites.
The program calls for the appointment of a supervisor tasked with assessing the site’s remaining productive potential, identifying the last operator, and determining the length of abandonment. Prospective participants would need to submit detailed legal documentation of their organizational structure, demonstrate operational expertise in mining, and provide profitability breakeven estimates for their ventures.
The fourth and final bill, HB 4513, also introduced by the bipartisan group led by McFall, focuses on the fiscal aspect of the HB 4512 initiative. The proposal would amend Michigan’s income tax laws to include proceeds generated from the proposed Bitcoin mining program.
The post Michigan: four bills on pension funds, CBDCs, and mining appeared first on Atlas21.
-
 @ 866e0139:6a9334e5
2025-05-22 06:51:15
@ 866e0139:6a9334e5
2025-05-22 06:51:15Autor: Milosz Matuschek. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie auch in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
https://www.youtube.com/watch?v=gjndTXyk3mw
Im Jahr 1954, als Frankreich gerade dabei war, seine kolonialen Kriege in Indochina und Algerien zu verschärfen, schrieb Boris Vian ein Lied – oder vielmehr: einen poetischen Faustschlag. Le Déserteur ist keine Ballade, sondern ein Manifest. Keine Hymne auf den Frieden, sondern eine Anklage gegen den Krieg. Adressiert an den Präsidenten, beginnt das Chanson wie ein höflicher Brief – und endet als flammender Akt des zivilen Ungehorsams.
„Herr Präsident,\ ich schreibe Ihnen einen Brief,\ den Sie vielleicht lesen werden,\ wenn Sie Zeit haben.“
Was folgt, ist ein klassischer Kriegsdienstverweigerungsbrief, aber eben kein bürokratischer. Vian spricht nicht in Paragraphen, sondern in Herzschlägen. Der Erzähler, ein einfacher Mann, will nicht kämpfen. Nicht für irgendein Vaterland, nicht für irgendeine Fahne, nicht für irgendeinen ideologischen Zweck.
„Ich soll zur Welt gekommen sein,\ um zu leben, nicht um zu sterben.“
70 Jahre später klingt diese Zeile wie ein Skandal. In einer Zeit, in der die Ukraine junge Männer für Kopfgeld auf der Straße zwangsrekrutiert und in Stahlgewitter schickt, in der palästinensische Jugendliche im Gazastreifen unter Trümmern begraben werden, während israelische Reservisten mit Dauerbefehl marschieren – ist Le Déserteur ein sakraler Text geworden. Fast ein Gebet.
„Wenn man mich verfolgt,\ werde ich den Gehorsam verweigern.\ Ich werde keine Waffe in die Hand nehmen,\ ich werde fliehen, bis ich Frieden finde.“
Wie viele „Deserteure“ gibt es heute, die wir gar nicht kennen? Menschen, die sich nicht auf die Seite der Bomben stellen wollen – egal, wer sie wirft? Die sich nicht mehr einspannen lassen zwischen Propaganda und Patriotismus? Die ihre Menschlichkeit über jeden nationalen Befehl stellen?
Der Krieg, sagt Vian, macht aus freien Menschen Befehlsempfänger und aus Söhnen Leichen. Und wer heute sagt, es gebe „gerechte Kriege“, sollte eine Frage beantworten: Ist es auch ein gerechter Tod?
Darum: Verweigert.
Verweigert den Befehl, zu hassen.\ Verweigert den Reflex, Partei zu ergreifen.\ Verweigert den Dienst an der Waffe.
Denn wie Vian singt:
„Sagen Sie's den Leuten:\ Ich werde nicht kommen.“
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 34ff86e0:dbb6b9fb
2025-05-25 02:36:39
@ 34ff86e0:dbb6b9fb
2025-05-25 02:36:39test openletter redirection after creation
-
 @ 04c915da:3dfbecc9
2025-05-15 15:31:45
@ 04c915da:3dfbecc9
2025-05-15 15:31:45Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ d360efec:14907b5f
2025-05-10 03:57:17
@ d360efec:14907b5f
2025-05-10 03:57:17Disclaimer: * การวิเคราะห์นี้เป็นเพียงแนวทาง ไม่ใช่คำแนะนำในการซื้อขาย * การลงทุนมีความเสี่ยง ผู้ลงทุนควรตัดสินใจด้วยตนเอง
-
 @ c1e9ab3a:9cb56b43
2025-05-09 23:10:14
@ c1e9ab3a:9cb56b43
2025-05-09 23:10:14I. Historical Foundations of U.S. Monetary Architecture
The early monetary system of the United States was built atop inherited commodity money conventions from Europe’s maritime economies. Silver and gold coins—primarily Spanish pieces of eight, Dutch guilders, and other foreign specie—formed the basis of colonial commerce. These units were already integrated into international trade and piracy networks and functioned with natural compatibility across England, France, Spain, and Denmark. Lacking a centralized mint or formal currency, the U.S. adopted these forms de facto.
As security risks and the practical constraints of physical coinage mounted, banks emerged to warehouse specie and issue redeemable certificates. These certificates evolved into fiduciary media—claims on specie not actually in hand. Banks observed over time that substantial portions of reserves remained unclaimed for years. This enabled fractional reserve banking: issuing more claims than reserves held, so long as redemption demand stayed low. The practice was inherently unstable, prone to panics and bank runs, prompting eventual centralization through the formation of the Federal Reserve in 1913.
Following the Civil War and unstable reinstatements of gold convertibility, the U.S. sought global monetary stability. After World War II, the Bretton Woods system formalized the U.S. dollar as the global reserve currency. The dollar was nominally backed by gold, but most international dollars were held offshore and recycled into U.S. Treasuries. The Nixon Shock of 1971 eliminated the gold peg, converting the dollar into pure fiat. Yet offshore dollar demand remained, sustained by oil trade mandates and the unique role of Treasuries as global reserve assets.
II. The Structure of Fiduciary Media and Treasury Demand
Under this system, foreign trade surpluses with the U.S. generate excess dollars. These surplus dollars are parked in U.S. Treasuries, thereby recycling trade imbalances into U.S. fiscal liquidity. While technically loans to the U.S. government, these purchases act like interest-only transfers—governments receive yield, and the U.S. receives spendable liquidity without principal repayment due in the short term. Debt is perpetually rolled over, rarely extinguished.
This creates an illusion of global subsidy: U.S. deficits are financed via foreign capital inflows that, in practice, function more like financial tribute systems than conventional debt markets. The underlying asset—U.S. Treasury debt—functions as the base reserve asset of the dollar system, replacing gold in post-Bretton Woods monetary logic.
III. Emergence of Tether and the Parastatal Dollar
Tether (USDT), as a private issuer of dollar-denominated tokens, mimics key central bank behaviors while operating outside the regulatory perimeter. It mints tokens allegedly backed 1:1 by U.S. dollars or dollar-denominated securities (mostly Treasuries). These tokens circulate globally, often in jurisdictions with limited banking access, and increasingly serve as synthetic dollar substitutes.
If USDT gains dominance as the preferred medium of exchange—due to technological advantages, speed, programmability, or access—it displaces Federal Reserve Notes (FRNs) not through devaluation, but through functional obsolescence. Gresham’s Law inverts: good money (more liquid, programmable, globally transferable USDT) displaces bad (FRNs) even if both maintain a nominal 1:1 parity.
Over time, this preference translates to a systemic demand shift. Actors increasingly use Tether instead of FRNs, especially in global commerce, digital marketplaces, or decentralized finance. Tether tokens effectively become shadow base money.
IV. Interaction with Commercial Banking and Redemption Mechanics
Under traditional fractional reserve systems, commercial banks issue loans denominated in U.S. dollars, expanding the money supply. When borrowers repay loans, this destroys the created dollars and contracts monetary elasticity. If borrowers repay in USDT instead of FRNs:
- Banks receive a non-Fed liability (USDT).
- USDT is not recognized as reserve-eligible within the Federal Reserve System.
- Banks must either redeem USDT for FRNs, or demand par-value conversion from Tether to settle reserve requirements and balance their books.
This places redemption pressure on Tether and threatens its 1:1 peg under stress. If redemption latency, friction, or cost arises, USDT’s equivalence to FRNs is compromised. Conversely, if banks are permitted or compelled to hold USDT as reserve or regulatory capital, Tether becomes a de facto reserve issuer.
In this scenario, banks may begin demanding loans in USDT, mirroring borrower behavior. For this to occur sustainably, banks must secure Tether liquidity. This creates two options: - Purchase USDT from Tether or on the secondary market, collateralized by existing fiat. - Borrow USDT directly from Tether, using bank-issued debt as collateral.
The latter mirrors Federal Reserve discount window operations. Tether becomes a lender of first resort, providing monetary elasticity to the banking system by creating new tokens against promissory assets—exactly how central banks function.
V. Structural Consequences: Parallel Central Banking
If Tether begins lending to commercial banks, issuing tokens backed by bank notes or collateralized debt obligations: - Tether controls the expansion of broad money through credit issuance. - Its balance sheet mimics a central bank, with Treasuries and bank debt as assets and tokens as liabilities. - It intermediates between sovereign debt and global liquidity demand, replacing the Federal Reserve’s open market operations with its own issuance-redemption cycles.
Simultaneously, if Tether purchases U.S. Treasuries with FRNs received through token issuance, it: - Supplies the Treasury with new liquidity (via bond purchases). - Collects yield on government debt. - Issues a parallel form of U.S. dollars that never require redemption—an interest-only loan to the U.S. government from a non-sovereign entity.
In this context, Tether performs monetary functions of both a central bank and a sovereign wealth fund, without political accountability or regulatory transparency.
VI. Endgame: Institutional Inversion and Fed Redundancy
This paradigm represents an institutional inversion:
- The Federal Reserve becomes a legacy issuer.
- Tether becomes the operational base money provider in both retail and interbank contexts.
- Treasuries remain the foundational reserve asset, but access to them is mediated by a private intermediary.
- The dollar persists, but its issuer changes. The State becomes a fiscal agent of a decentralized financial ecosystem, not its monetary sovereign.
Unless the Federal Reserve reasserts control—either by absorbing Tether, outlawing its instruments, or integrating its tokens into the reserve framework—it risks becoming irrelevant in the daily function of money.
Tether, in this configuration, is no longer a derivative of the dollar—it is the dollar, just one level removed from sovereign control. The future of monetary sovereignty under such a regime is post-national and platform-mediated.
-
 @ 6389be64:ef439d32
2025-05-24 21:51:47
@ 6389be64:ef439d32
2025-05-24 21:51:47Most nematodes are beneficial and "graze" on black vine weevil, currant borer moth, fungus gnats, other weevils, scarabs, cutworms, webworms, billbugs, mole crickets, termites, peach tree borer and carpenter worm moths.
They also predate bacteria, recycling nutrients back into the soil and by doing so stimulates bacterial activity. They act as microbial taxis by transporting microbes to new locations of soil as they move through it while providing aeration.
https://stacker.news/items/988573
-
 @ 23b0e2f8:d8af76fc
2025-01-08 18:17:52
@ 23b0e2f8:d8af76fc
2025-01-08 18:17:52Necessário
- Um Android que você não use mais (a câmera deve estar funcionando).
- Um cartão microSD (opcional, usado apenas uma vez).
- Um dispositivo para acompanhar seus fundos (provavelmente você já tem um).
Algumas coisas que você precisa saber
- O dispositivo servirá como um assinador. Qualquer movimentação só será efetuada após ser assinada por ele.
- O cartão microSD será usado para transferir o APK do Electrum e garantir que o aparelho não terá contato com outras fontes de dados externas após sua formatação. Contudo, é possível usar um cabo USB para o mesmo propósito.
- A ideia é deixar sua chave privada em um dispositivo offline, que ficará desligado em 99% do tempo. Você poderá acompanhar seus fundos em outro dispositivo conectado à internet, como seu celular ou computador pessoal.
O tutorial será dividido em dois módulos:
- Módulo 1 - Criando uma carteira fria/assinador.
- Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.
No final, teremos:
- Uma carteira fria que também servirá como assinador.
- Um dispositivo para acompanhar os fundos da carteira.

Módulo 1 - Criando uma carteira fria/assinador
-
Baixe o APK do Electrum na aba de downloads em https://electrum.org/. Fique à vontade para verificar as assinaturas do software, garantindo sua autenticidade.
-
Formate o cartão microSD e coloque o APK do Electrum nele. Caso não tenha um cartão microSD, pule este passo.

- Retire os chips e acessórios do aparelho que será usado como assinador, formate-o e aguarde a inicialização.

- Durante a inicialização, pule a etapa de conexão ao Wi-Fi e rejeite todas as solicitações de conexão. Após isso, você pode desinstalar aplicativos desnecessários, pois precisará apenas do Electrum. Certifique-se de que Wi-Fi, Bluetooth e dados móveis estejam desligados. Você também pode ativar o modo avião.\ (Curiosidade: algumas pessoas optam por abrir o aparelho e danificar a antena do Wi-Fi/Bluetooth, impossibilitando essas funcionalidades.)

- Insira o cartão microSD com o APK do Electrum no dispositivo e instale-o. Será necessário permitir instalações de fontes não oficiais.

- No Electrum, crie uma carteira padrão e gere suas palavras-chave (seed). Anote-as em um local seguro. Caso algo aconteça com seu assinador, essas palavras permitirão o acesso aos seus fundos novamente. (Aqui entra seu método pessoal de backup.)

Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.
-
Criar uma carteira somente leitura em outro dispositivo, como seu celular ou computador pessoal, é uma etapa bastante simples. Para este tutorial, usaremos outro smartphone Android com Electrum. Instale o Electrum a partir da aba de downloads em https://electrum.org/ ou da própria Play Store. (ATENÇÃO: O Electrum não existe oficialmente para iPhone. Desconfie se encontrar algum.)
-
Após instalar o Electrum, crie uma carteira padrão, mas desta vez escolha a opção Usar uma chave mestra.

- Agora, no assinador que criamos no primeiro módulo, exporte sua chave pública: vá em Carteira > Detalhes da carteira > Compartilhar chave mestra pública.

-
Escaneie o QR gerado da chave pública com o dispositivo de consulta. Assim, ele poderá acompanhar seus fundos, mas sem permissão para movimentá-los.
-
Para receber fundos, envie Bitcoin para um dos endereços gerados pela sua carteira: Carteira > Addresses/Coins.
-
Para movimentar fundos, crie uma transação no dispositivo de consulta. Como ele não possui a chave privada, será necessário assiná-la com o dispositivo assinador.

- No assinador, escaneie a transação não assinada, confirme os detalhes, assine e compartilhe. Será gerado outro QR, desta vez com a transação já assinada.

- No dispositivo de consulta, escaneie o QR da transação assinada e transmita-a para a rede.
Conclusão
Pontos positivos do setup:
- Simplicidade: Basta um dispositivo Android antigo.
- Flexibilidade: Funciona como uma ótima carteira fria, ideal para holders.
Pontos negativos do setup:
- Padronização: Não utiliza seeds no padrão BIP-39, você sempre precisará usar o electrum.
- Interface: A aparência do Electrum pode parecer antiquada para alguns usuários.
Nesse ponto, temos uma carteira fria que também serve para assinar transações. O fluxo de assinar uma transação se torna: Gerar uma transação não assinada > Escanear o QR da transação não assinada > Conferir e assinar essa transação com o assinador > Gerar QR da transação assinada > Escanear a transação assinada com qualquer outro dispositivo que possa transmiti-la para a rede.
Como alguns devem saber, uma transação assinada de Bitcoin é praticamente impossível de ser fraudada. Em um cenário catastrófico, você pode mesmo que sem internet, repassar essa transação assinada para alguém que tenha acesso à rede por qualquer meio de comunicação. Mesmo que não queiramos que isso aconteça um dia, esse setup acaba por tornar essa prática possível.
-
 @ eb0157af:77ab6c55
2025-05-25 04:48:10
@ eb0157af:77ab6c55
2025-05-25 04:48:10A fake Uber driver steals $73,000 in XRP and $50,000 in Bitcoin after drugging an American tourist.
A U.S. citizen vacationing in the United Kingdom fell victim to a scam that cost him $123,000 in cryptocurrencies stored on his smartphone. The man was drugged by an individual posing as an Uber driver.
According to My London, Jacob Irwin-Cline had spent the evening at a London nightclub, consuming several alcoholic drinks before requesting an Uber ride home. The victim admitted he hadn’t carefully verified the booking details on his device, mistakenly getting into a private taxi driven by someone who, at first glance, resembled the expected Uber driver but was using a completely different vehicle.
Once inside the car, the American tourist reported that the driver offered him a cigarette, allegedly laced with scopolamine — a rare and powerful sedative. Irwin-Cline described how the smoke made him extremely docile and fatigued, causing him to lose consciousness for around half an hour.
Upon waking, the driver ordered the victim to get out of the vehicle. As Irwin-Cline stepped out, the man suddenly accelerated, running him over and fleeing with his mobile phone, which contained the private keys and access to his cryptocurrencies. Screenshots provided to MyLondon show that $73,000 worth of XRP and $50,000 in bitcoin had been transferred to various wallets.
This incident adds to a growing trend of kidnappings, extortions, armed robberies, and ransom attempts targeting crypto executives, investors, and their families.
Just a few weeks ago, the daughter and grandson of Pierre Noizat, CEO of crypto exchange Paymium, were targeted in a kidnapping attempt in Paris. The incident took place in broad daylight when attackers tried to force the family into a parked vehicle. However, Noizat’s daughter managed to fight off the assailants.
The post American tourist drugged and robbed: $123,000 in crypto stolen in London appeared first on Atlas21.
-
 @ 207ad2a0:e7cca7b0
2025-01-07 03:46:04
@ 207ad2a0:e7cca7b0
2025-01-07 03:46:04Quick context: I wanted to check out Nostr's longform posts and this blog post seemed like a good one to try and mirror. It's originally from my free to read/share attempt to write a novel, but this post here is completely standalone - just describing how I used AI image generation to make a small piece of the work.
Hold on, put your pitchforks down - outside of using Grammerly & Emacs for grammatical corrections - not a single character was generated or modified by computers; a non-insignificant portion of my first draft originating on pen & paper. No AI is ~~weird and crazy~~ imaginative enough to write like I do. The only successful AI contribution you'll find is a single image, the map, which I heavily edited. This post will go over how I generated and modified an image using AI, which I believe brought some value to the work, and cover a few quick thoughts about AI towards the end.
Let's be clear, I can't draw, but I wanted a map which I believed would improve the story I was working on. After getting abysmal results by prompting AI with text only I decided to use "Diffuse the Rest," a Stable Diffusion tool that allows you to provide a reference image + description to fine tune what you're looking for. I gave it this Microsoft Paint looking drawing:
and after a number of outputs, selected this one to work on:
The image is way better than the one I provided, but had I used it as is, I still feel it would have decreased the quality of my work instead of increasing it. After firing up Gimp I cropped out the top and bottom, expanded the ocean and separated the landmasses, then copied the top right corner of the large landmass to replace the bottom left that got cut off. Now we've got something that looks like concept art: not horrible, and gets the basic idea across, but it's still due for a lot more detail.

The next thing I did was add some texture to make it look more map like. I duplicated the layer in Gimp and applied the "Cartoon" filter to both for some texture. The top layer had a much lower effect strength to give it a more textured look, while the lower layer had a higher effect strength that looked a lot like mountains or other terrain features. Creating a layer mask allowed me to brush over spots to display the lower layer in certain areas, giving it some much needed features.
At this point I'd made it to where I felt it may improve the work instead of detracting from it - at least after labels and borders were added, but the colors seemed artificial and out of place. Luckily, however, this is when PhotoFunia could step in and apply a sketch effect to the image.
At this point I was pretty happy with how it was looking, it was close to what I envisioned and looked very visually appealing while still being a good way to portray information. All that was left was to make the white background transparent, add some minor details, and add the labels and borders. Below is the exact image I wound up using:

Overall, I'm very satisfied with how it turned out, and if you're working on a creative project, I'd recommend attempting something like this. It's not a central part of the work, but it improved the chapter a fair bit, and was doable despite lacking the talent and not intending to allocate a budget to my making of a free to read and share story.
The AI Generated Elephant in the Room
If you've read my non-fiction writing before, you'll know that I think AI will find its place around the skill floor as opposed to the skill ceiling. As you saw with my input, I have absolutely zero drawing talent, but with some elbow grease and an existing creative direction before and after generating an image I was able to get something well above what I could have otherwise accomplished. Outside of the lowest common denominators like stock photos for the sole purpose of a link preview being eye catching, however, I doubt AI will be wholesale replacing most creative works anytime soon. I can assure you that I tried numerous times to describe the map without providing a reference image, and if I used one of those outputs (or even just the unedited output after providing the reference image) it would have decreased the quality of my work instead of improving it.
I'm going to go out on a limb and expect that AI image, text, and video is all going to find its place in slop & generic content (such as AI generated slop replacing article spinners and stock photos respectively) and otherwise be used in a supporting role for various creative endeavors. For people working on projects like I'm working on (e.g. intended budget $0) it's helpful to have an AI capable of doing legwork - enabling projects to exist or be improved in ways they otherwise wouldn't have. I'm also guessing it'll find its way into more professional settings for grunt work - think a picture frame or fake TV show that would exist in the background of an animated project - likely a detail most people probably wouldn't notice, but that would save the creators time and money and/or allow them to focus more on the essential aspects of said work. Beyond that, as I've predicted before: I expect plenty of emails will be generated from a short list of bullet points, only to be summarized by the recipient's AI back into bullet points.
I will also make a prediction counter to what seems mainstream: AI is about to peak for a while. The start of AI image generation was with Google's DeepDream in 2015 - image recognition software that could be run in reverse to "recognize" patterns where there were none, effectively generating an image from digital noise or an unrelated image. While I'm not an expert by any means, I don't think we're too far off from that a decade later, just using very fine tuned tools that develop more coherent images. I guess that we're close to maxing out how efficiently we're able to generate images and video in that manner, and the hard caps on how much creative direction we can have when using AI - as well as the limits to how long we can keep it coherent (e.g. long videos or a chronologically consistent set of images) - will prevent AI from progressing too far beyond what it is currently unless/until another breakthrough occurs.
-
 @ eb0157af:77ab6c55
2025-05-25 04:48:09
@ eb0157af:77ab6c55
2025-05-25 04:48:09Banking giants JPMorgan, Bank of America, Citigroup, and Wells Fargo are in talks to develop a unified stablecoin solution.
According to the Wall Street Journal on May 22, some of the largest financial institutions in the United States are exploring the possibility of joining forces to launch a stablecoin.
Subsidiaries of JPMorgan, Bank of America, Citigroup, and Wells Fargo have initiated preliminary discussions for a joint stablecoin issuance, according to sources close to the matter cited by the WSJ. Also at the negotiating table are Early Warning Services, the parent company of the digital payments network Zelle, and the payment network Clearing House.
The talks are reportedly still in the early stages, and any final decision could change depending on regulatory developments and market demand for stablecoins.
Stablecoin regulation
On May 20, the US Senate voted 66 to 32 to advance discussion of the Guiding and Establishing National Innovation for US Stablecoins Act (GENIUS Act), a specific law to regulate stablecoins. The bill outlines a regulatory framework for stablecoin collateralization and mandates compliance with anti-money laundering rules.
David Sacks, White House crypto advisor, expressed optimism about the bill’s bipartisan approval. However, senior Democratic Party officials intend to amend the bill to include a clause preventing former President Donald Trump and other US officials from profiting from stablecoins.
Demand for stablecoins has increased, with total market capitalization rising to $245 billion from $205 billion at the beginning of the year, a 20% increase.
The post Major US banks consider launching a joint stablecoin appeared first on Atlas21.
-
 @ 04c915da:3dfbecc9
2025-03-26 20:54:33
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 3283ef81:0a531a33
2025-05-24 20:47:39
@ 3283ef81:0a531a33
2025-05-24 20:47:39This event has been deleted; your client is ignoring the delete request.
-
 @ e6817453:b0ac3c39
2025-01-05 14:29:17
@ e6817453:b0ac3c39
2025-01-05 14:29:17The Rise of Graph RAGs and the Quest for Data Quality
As we enter a new year, it’s impossible to ignore the boom of retrieval-augmented generation (RAG) systems, particularly those leveraging graph-based approaches. The previous year saw a surge in advancements and discussions about Graph RAGs, driven by their potential to enhance large language models (LLMs), reduce hallucinations, and deliver more reliable outputs. Let’s dive into the trends, challenges, and strategies for making the most of Graph RAGs in artificial intelligence.
Booming Interest in Graph RAGs
Graph RAGs have dominated the conversation in AI circles. With new research papers and innovations emerging weekly, it’s clear that this approach is reshaping the landscape. These systems, especially those developed by tech giants like Microsoft, demonstrate how graphs can:
- Enhance LLM Outputs: By grounding responses in structured knowledge, graphs significantly reduce hallucinations.
- Support Complex Queries: Graphs excel at managing linked and connected data, making them ideal for intricate problem-solving.
Conferences on linked and connected data have increasingly focused on Graph RAGs, underscoring their central role in modern AI systems. However, the excitement around this technology has brought critical questions to the forefront: How do we ensure the quality of the graphs we’re building, and are they genuinely aligned with our needs?
Data Quality: The Foundation of Effective Graphs
A high-quality graph is the backbone of any successful RAG system. Constructing these graphs from unstructured data requires attention to detail and rigorous processes. Here’s why:
- Richness of Entities: Effective retrieval depends on graphs populated with rich, detailed entities.
- Freedom from Hallucinations: Poorly constructed graphs amplify inaccuracies rather than mitigating them.
Without robust data quality, even the most sophisticated Graph RAGs become ineffective. As a result, the focus must shift to refining the graph construction process. Improving data strategy and ensuring meticulous data preparation is essential to unlock the full potential of Graph RAGs.
Hybrid Graph RAGs and Variations
While standard Graph RAGs are already transformative, hybrid models offer additional flexibility and power. Hybrid RAGs combine structured graph data with other retrieval mechanisms, creating systems that:
- Handle diverse data sources with ease.
- Offer improved adaptability to complex queries.
Exploring these variations can open new avenues for AI systems, particularly in domains requiring structured and unstructured data processing.
Ontology: The Key to Graph Construction Quality
Ontology — defining how concepts relate within a knowledge domain — is critical for building effective graphs. While this might sound abstract, it’s a well-established field blending philosophy, engineering, and art. Ontology engineering provides the framework for:
- Defining Relationships: Clarifying how concepts connect within a domain.
- Validating Graph Structures: Ensuring constructed graphs are logically sound and align with domain-specific realities.
Traditionally, ontologists — experts in this discipline — have been integral to large enterprises and research teams. However, not every team has access to dedicated ontologists, leading to a significant challenge: How can teams without such expertise ensure the quality of their graphs?
How to Build Ontology Expertise in a Startup Team
For startups and smaller teams, developing ontology expertise may seem daunting, but it is achievable with the right approach:
- Assign a Knowledge Champion: Identify a team member with a strong analytical mindset and give them time and resources to learn ontology engineering.
- Provide Training: Invest in courses, workshops, or certifications in knowledge graph and ontology creation.
- Leverage Partnerships: Collaborate with academic institutions, domain experts, or consultants to build initial frameworks.
- Utilize Tools: Introduce ontology development tools like Protégé, OWL, or SHACL to simplify the creation and validation process.
- Iterate with Feedback: Continuously refine ontologies through collaboration with domain experts and iterative testing.
So, it is not always affordable for a startup to have a dedicated oncologist or knowledge engineer in a team, but you could involve consulters or build barefoot experts.
You could read about barefoot experts in my article :
Even startups can achieve robust and domain-specific ontology frameworks by fostering in-house expertise.
How to Find or Create Ontologies
For teams venturing into Graph RAGs, several strategies can help address the ontology gap:
-
Leverage Existing Ontologies: Many industries and domains already have open ontologies. For instance:
-
Public Knowledge Graphs: Resources like Wikipedia’s graph offer a wealth of structured knowledge.
- Industry Standards: Enterprises such as Siemens have invested in creating and sharing ontologies specific to their fields.
-
Business Framework Ontology (BFO): A valuable resource for enterprises looking to define business processes and structures.
-
Build In-House Expertise: If budgets allow, consider hiring knowledge engineers or providing team members with the resources and time to develop expertise in ontology creation.
-
Utilize LLMs for Ontology Construction: Interestingly, LLMs themselves can act as a starting point for ontology development:
-
Prompt-Based Extraction: LLMs can generate draft ontologies by leveraging their extensive training on graph data.
- Domain Expert Refinement: Combine LLM-generated structures with insights from domain experts to create tailored ontologies.
Parallel Ontology and Graph Extraction
An emerging approach involves extracting ontologies and graphs in parallel. While this can streamline the process, it presents challenges such as:
- Detecting Hallucinations: Differentiating between genuine insights and AI-generated inaccuracies.
- Ensuring Completeness: Ensuring no critical concepts are overlooked during extraction.
Teams must carefully validate outputs to ensure reliability and accuracy when employing this parallel method.
LLMs as Ontologists
While traditionally dependent on human expertise, ontology creation is increasingly supported by LLMs. These models, trained on vast amounts of data, possess inherent knowledge of many open ontologies and taxonomies. Teams can use LLMs to:
- Generate Skeleton Ontologies: Prompt LLMs with domain-specific information to draft initial ontology structures.
- Validate and Refine Ontologies: Collaborate with domain experts to refine these drafts, ensuring accuracy and relevance.
However, for validation and graph construction, formal tools such as OWL, SHACL, and RDF should be prioritized over LLMs to minimize hallucinations and ensure robust outcomes.
Final Thoughts: Unlocking the Power of Graph RAGs
The rise of Graph RAGs underscores a simple but crucial correlation: improving graph construction and data quality directly enhances retrieval systems. To truly harness this power, teams must invest in understanding ontologies, building quality graphs, and leveraging both human expertise and advanced AI tools.
As we move forward, the interplay between Graph RAGs and ontology engineering will continue to shape the future of AI. Whether through adopting existing frameworks or exploring innovative uses of LLMs, the path to success lies in a deep commitment to data quality and domain understanding.
Have you explored these technologies in your work? Share your experiences and insights — and stay tuned for more discussions on ontology extraction and its role in AI advancements. Cheers to a year of innovation!
-
 @ 211c0393:e9262c4d
2025-05-25 04:00:34
@ 211c0393:e9262c4d
2025-05-25 04:00:34Original: https://www.yakihonne.com/article/naddr1qvzqqqr4gupzqgguqwf52cyve89xnxc4eh95jklelgw646kkkcdhxm4fp05jvtzdqq2hj6fhtpqkuutdv4xxxazjv9t92atedev45mcwusz
Nihon no kakuseizai Nihon no kakusei-zai bijinesu no yami: Keisatsu, bōryokudan, soshite
chinmoku no kyōhan kankei' no shinsō** 1. Bōryokudan no shihai kōzō (kōteki dēta ni motodzuku) yunyū izon no riyū: Kokunai seizō wa kon'nan (Heisei 6-nenkakusei-zai genryō kisei-hō' de kisei kyōka)→ myanmā Chūgoku kara no mitsuyu ga shuryū (Kokuren yakubutsu hanzai jimushoWorld Drug Report 2023'). Bōryokudan no rieki-ritsu: 1 Kg-atari shiire kakaku 30 man-en → kouri kakaku 500 man ~ 1000 man-en (Keisatsuchōyakubutsu jōsei hōkoku-sho' 2022-nen). 2. Keisatsu to bōryokudan nokyōsei kankei' taiho tōkei no fushizen-sa: Zen yakubutsu taiho-sha no 70-pāsento ga tanjun shoji (kōsei Rōdōshōyakubutsu ran'yō jōkyō' 2023-nen). Mitsuyu soshiki no tekihatsu wa zentai no 5-pāsento-miman (tōkyōchikentokusōbu dēta). Media no kenshō: NHK supesharukakusei-zai sensō'(2021-nen) de shiteki sa retamattan yūzā yūsen sōsa' no jittai. 3. Mujun suru genjitsu juyō no fukashi-sei: G 7 de saikō no kakusei-zai kakaku (1 g-atari 3 ~ 7 man-en, Ō kome no 3-bai)→ bōryokudan no bōri (Zaimushōsoshiki hanzai shikin ryūdō chōsa'). Shiyōsha-ritsu wa hikui (jinkō no 0. 2%, Kokuren chōsa) ga, taiho-sha no kahansū o shimeru mujun. 4.Mitsuyu soshiki taisaku' no genkai kokusai-tekina shippai rei: Mekishiko (karuteru tekihatsu-go mo ichiba kakudai), Ōshū (gōsei yakubutsu no man'en)→ daitai soshiki ga sokuza ni taitō (Eiekonomisuto' 2023-nen 6 tsuki-gō). Nippon'nochiri-teki hande: Kaijō mitsuyu no tekihatsu-ritsu wa 10-pāsento-miman (Kaijōhoanchō hōkoku). 5. Kaiketsusaku no saikō (jijitsu ni motodzuku teian) ADHD chiryō-yaku no gōhō-ka: Amerika seishin'igakukaiADHD kanja no 60-pāsento ga jiko chiryō de ihō yakubutsu shiyō'(2019-nen kenkyū). Nihonde wa ritarin aderōru kinshi → bōryokudan no ichiba dokusen. Rōdō kankyō kaikaku: Karō-shi rain koe no rōdō-sha 20-pāsento (Kōrōshōrōdō jikan chōsa' 2023-nen)→ kakusei-zai juyō no ichiin. 6. Kokuhatsu no risuku to jōhō-gen tokumei-sei no jūyō-sei: Kako no bōryokudan hōfuku jirei (2018-nen, kokuhatsu kisha e no kyōhaku jiken Mainichishinbun hōdō). Kōteki dēta nomi in'yō: Rei:Keisatsuchō tōkei'Kokuren hōkoku-sho' nado daisansha kenshō kanōna jōhō. Ketsuron: Henkaku no tame ni wajijitsu' no kajika ga hitsuyō `yakubutsu = kojin no dōtokuteki mondai' to iu gensō ga, bōryokudan to fuhai kanryō o ri shite iru. Kokusai dēta to kokunai tōkei no mujun o tsuku koto de, shisutemu no giman o abakeru. Anzen'na kyōyū no tame ni: Kojin tokutei o sake, tokumei purattofōmu (tōa-jō fōramu-tō) de giron. Kōteki kikan no dēta o chokusetsu rinku (rei: Keisatsuchō PDF repōto). Kono bunsho wa, kōhyō sa reta tōkei media hōdō nomi o konkyo to shi, kojin no suisoku o haijo shite imasu. Kyōi o yokeru tame, gutaitekina kojin soshiki no hinan wa itotekini sakete imasu. Show more 1,321 / 5,000 Stimulants in Japan The dark side of the Japanese stimulant drug business:The truth about the police, the yakuza, and their "silent complicity"**
- The control structure of the yakuza (based on public data)
Reasons for dependence on imports: Domestic production is difficult (tightened regulations under the Stimulant Drug Raw Materials Control Act of 1994) → Smuggling from Myanmar and China is the norm (UNODC World Drug Report 2023).
Profit margins for yakuza: Purchase price of 300,000 yen per kg → Retail price of 5 to 10 million yen (National Police Agency Drug Situation Report 2022).
- The "symbiotic relationship" between the police and the yakuza
The unnaturalness of arrest statistics: 70% of all drug arrests are for simple possession (Ministry of Health, Labor and Welfare Drug Abuse Situation 2023). Smuggling organizations account for less than 5% of all arrests (Tokyo District Public Prosecutors Office Special Investigation Unit data). Media verification: The reality of "end-user priority investigation" pointed out in the NHK special "Stimulant War" (2021).
- Contradictory reality
Invisibility of demand: The highest stimulant drug price in the G7 (30,000 to 70,000 yen per gram, three times that of Europe and the United States) → Excessive profits by organized crime (Ministry of Finance "Survey on Organized Crime Fund Flows"). The contradiction that the user rate is low (0.2% of the population, UN survey), but accounts for the majority of arrests.
- The limits of "countermeasures against smuggling organizations"
International examples of failure: Mexico (market expands even after cartel crackdown), Europe (proliferation of synthetic drugs) → Alternative organizations immediately emerge (UK "The Economist" June 2023 issue). Japan's geographical handicap: The crackdown rate for maritime smuggling is less than 10% (Japan Coast Guard report).
- Rethinking solutions (fact-based proposals)
Legalization of ADHD medications:
American Psychiatric Association: "60% of ADHD patients self-medicate with illegal drugs" (2019 study).
Banning Ritalin and Adderall in Japan → Yakuza monopoly on the market.
Work environment reform:
20% of workers exceed the line of death from overwork (Ministry of Health, Labor and Welfare "Working Hours Survey" 2023) → One cause of stimulant drug demand.
- Risks of accusation and sources of information
Importance of anonymity:
Past cases of Yakuza retaliation (2018, threat against accusing journalist, reported in the Mainichi Shimbun).
Citing only public data:
Examples: Information that can be verified by a third party, such as "National Police Agency statistics" and "UN reports".
Conclusion: Visualization of "facts" is necessary for change
The illusion that "drugs = individual moral problems" benefits Yakuza and corrupt bureaucrats.
Pointing out the contradictions between international data and domestic statistics can expose the deception of the system.
For safe sharing:
Avoid identifying individuals and discuss on anonymous platforms (such as forums on Tor).
Direct links to data from public organizations (e.g. National Police Agency PDF report).
This document is based solely on published statistics and media reports, and excludes personal speculation.
To avoid threats, we have intentionally avoided blaming specific individuals or organizations. Send feedback
-
 @ 04c915da:3dfbecc9
2025-03-25 17:43:44
@ 04c915da:3dfbecc9
2025-03-25 17:43:44One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ a4a6b584:1e05b95b
2025-01-02 18:13:31
@ a4a6b584:1e05b95b
2025-01-02 18:13:31The Four-Layer Framework
Layer 1: Zoom Out

Start by looking at the big picture. What’s the subject about, and why does it matter? Focus on the overarching ideas and how they fit together. Think of this as the 30,000-foot view—it’s about understanding the "why" and "how" before diving into the "what."
Example: If you’re learning programming, start by understanding that it’s about giving logical instructions to computers to solve problems.
- Tip: Keep it simple. Summarize the subject in one or two sentences and avoid getting bogged down in specifics at this stage.
Once you have the big picture in mind, it’s time to start breaking it down.
Layer 2: Categorize and Connect

Now it’s time to break the subject into categories—like creating branches on a tree. This helps your brain organize information logically and see connections between ideas.
Example: Studying biology? Group concepts into categories like cells, genetics, and ecosystems.
- Tip: Use headings or labels to group similar ideas. Jot these down in a list or simple diagram to keep track.
With your categories in place, you’re ready to dive into the details that bring them to life.
Layer 3: Master the Details

Once you’ve mapped out the main categories, you’re ready to dive deeper. This is where you learn the nuts and bolts—like formulas, specific techniques, or key terminology. These details make the subject practical and actionable.
Example: In programming, this might mean learning the syntax for loops, conditionals, or functions in your chosen language.
- Tip: Focus on details that clarify the categories from Layer 2. Skip anything that doesn’t add to your understanding.
Now that you’ve mastered the essentials, you can expand your knowledge to include extra material.
Layer 4: Expand Your Horizons

Finally, move on to the extra material—less critical facts, trivia, or edge cases. While these aren’t essential to mastering the subject, they can be useful in specialized discussions or exams.
Example: Learn about rare programming quirks or historical trivia about a language’s development.
- Tip: Spend minimal time here unless it’s necessary for your goals. It’s okay to skim if you’re short on time.
Pro Tips for Better Learning
1. Use Active Recall and Spaced Repetition
Test yourself without looking at notes. Review what you’ve learned at increasing intervals—like after a day, a week, and a month. This strengthens memory by forcing your brain to actively retrieve information.
2. Map It Out
Create visual aids like diagrams or concept maps to clarify relationships between ideas. These are particularly helpful for organizing categories in Layer 2.
3. Teach What You Learn
Explain the subject to someone else as if they’re hearing it for the first time. Teaching exposes any gaps in your understanding and helps reinforce the material.
4. Engage with LLMs and Discuss Concepts
Take advantage of tools like ChatGPT or similar large language models to explore your topic in greater depth. Use these tools to:
- Ask specific questions to clarify confusing points.
- Engage in discussions to simulate real-world applications of the subject.
- Generate examples or analogies that deepen your understanding.Tip: Use LLMs as a study partner, but don’t rely solely on them. Combine these insights with your own critical thinking to develop a well-rounded perspective.
Get Started
Ready to try the Four-Layer Method? Take 15 minutes today to map out the big picture of a topic you’re curious about—what’s it all about, and why does it matter? By building your understanding step by step, you’ll master the subject with less stress and more confidence.
-
 @ fd208ee8:0fd927c1
2024-12-26 07:02:59
@ fd208ee8:0fd927c1
2024-12-26 07:02:59I just read this, and found it enlightening.
Jung... notes that intelligence can be seen as problem solving at an everyday level..., whereas creativity may represent problem solving for less common issues
Other studies have used metaphor creation as a creativity measure instead of divergent thinking and a spectrum of CHC components instead of just g and have found much higher relationships between creativity and intelligence than past studies
https://www.mdpi.com/2079-3200/3/3/59
I'm unusually intelligent (Who isn't?), but I'm much more creative, than intelligent, and I think that confuses people. The ability to apply intelligence, to solve completely novel problems, on the fly, is something IQ tests don't even claim to measure. They just claim a correlation.
Creativity requires taking wild, mental leaps out into nothingness; simply trusting that your brain will land you safely. And this is why I've been at the forefront of massive innovation, over and over, but never got rich off of it.
I'm a starving autist.
Zaps are the first time I've ever made money directly, for solving novel problems. Companies don't do this because there is a span of time between providing a solution and the solution being implemented, and the person building the implementation (or their boss) receives all the credit for the existence of the solution. At best, you can hope to get pawned off with a small bonus.
Nobody can remember who came up with the solution, originally, and that person might not even be there, anymore, and probably never filed a patent, and may have no idea that their idea has even been built. They just run across it, later, in a tech magazine or museum, and say, "Well, will you look at that! Someone actually went and built it! Isn't that nice!"
Universities at least had the idea of cementing novel solutions in academic papers, but that: 1) only works if you're an academic, and at a university, 2) is an incredibly slow process, not appropriate for a truly innovative field, 3) leads to manifestations of perverse incentives and biased research frameworks, coming from 'publish or perish' policies.
But I think long-form notes and zaps solve for this problem. #Alexandria, especially, is being built to cater to this long-suffering class of chronic underachievers. It leaves a written, public, time-stamped record of Clever Ideas We Have Had.
Because they are clever, the ideas. And we have had them.
-
 @ fe32298e:20516265
2024-12-16 20:59:13
@ fe32298e:20516265
2024-12-16 20:59:13Today I learned how to install NVapi to monitor my GPUs in Home Assistant.
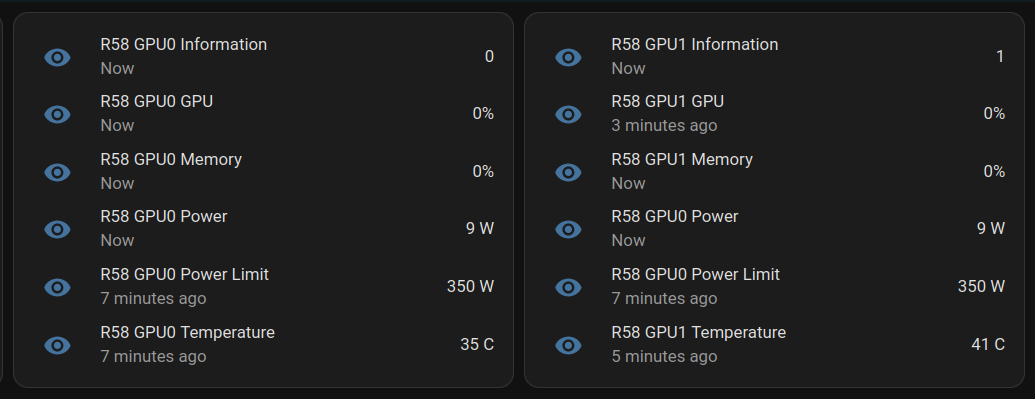
NVApi is a lightweight API designed for monitoring NVIDIA GPU utilization and enabling automated power management. It provides real-time GPU metrics, supports integration with tools like Home Assistant, and offers flexible power management and PCIe link speed management based on workload and thermal conditions.
- GPU Utilization Monitoring: Utilization, memory usage, temperature, fan speed, and power consumption.
- Automated Power Limiting: Adjusts power limits dynamically based on temperature thresholds and total power caps, configurable per GPU or globally.
- Cross-GPU Coordination: Total power budget applies across multiple GPUs in the same system.
- PCIe Link Speed Management: Controls minimum and maximum PCIe link speeds with idle thresholds for power optimization.
- Home Assistant Integration: Uses the built-in RESTful platform and template sensors.
Getting the Data
sudo apt install golang-go git clone https://github.com/sammcj/NVApi.git cd NVapi go run main.go -port 9999 -rate 1 curl http://localhost:9999/gpuResponse for a single GPU:
[ { "index": 0, "name": "NVIDIA GeForce RTX 4090", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 16, "power_limit_watts": 450, "memory_total_gb": 23.99, "memory_used_gb": 0.46, "memory_free_gb": 23.52, "memory_usage_percent": 2, "temperature": 38, "processes": [], "pcie_link_state": "not managed" } ]Response for multiple GPUs:
[ { "index": 0, "name": "NVIDIA GeForce RTX 3090", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 14, "power_limit_watts": 350, "memory_total_gb": 24, "memory_used_gb": 0.43, "memory_free_gb": 23.57, "memory_usage_percent": 2, "temperature": 36, "processes": [], "pcie_link_state": "not managed" }, { "index": 1, "name": "NVIDIA RTX A4000", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 10, "power_limit_watts": 140, "memory_total_gb": 15.99, "memory_used_gb": 0.56, "memory_free_gb": 15.43, "memory_usage_percent": 3, "temperature": 41, "processes": [], "pcie_link_state": "not managed" } ]Start at Boot
Create
/etc/systemd/system/nvapi.service:``` [Unit] Description=Run NVapi After=network.target
[Service] Type=simple Environment="GOPATH=/home/ansible/go" WorkingDirectory=/home/ansible/NVapi ExecStart=/usr/bin/go run main.go -port 9999 -rate 1 Restart=always User=ansible
Environment="GPU_TEMP_CHECK_INTERVAL=5"
Environment="GPU_TOTAL_POWER_CAP=400"
Environment="GPU_0_LOW_TEMP=40"
Environment="GPU_0_MEDIUM_TEMP=70"
Environment="GPU_0_LOW_TEMP_LIMIT=135"
Environment="GPU_0_MEDIUM_TEMP_LIMIT=120"
Environment="GPU_0_HIGH_TEMP_LIMIT=100"
Environment="GPU_1_LOW_TEMP=45"
Environment="GPU_1_MEDIUM_TEMP=75"
Environment="GPU_1_LOW_TEMP_LIMIT=140"
Environment="GPU_1_MEDIUM_TEMP_LIMIT=125"
Environment="GPU_1_HIGH_TEMP_LIMIT=110"
[Install] WantedBy=multi-user.target ```
Home Assistant
Add to Home Assistant
configuration.yamland restart HA (completely).For a single GPU, this works: ``` sensor: - platform: rest name: MYPC GPU Information resource: http://mypc:9999 method: GET headers: Content-Type: application/json value_template: "{{ value_json[0].index }}" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature scan_interval: 1 # seconds
- platform: template sensors: mypc_gpu_0_gpu: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} GPU" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_memory: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Memory" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_power: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Power" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_0_power_limit: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_0_temperature: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Temperature" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'temperature') }}" unit_of_measurement: "°C" ```
For multiple GPUs: ``` rest: scan_interval: 1 resource: http://mypc:9999 sensor: - name: "MYPC GPU0 Information" value_template: "{{ value_json[0].index }}" json_attributes_path: "$.0" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature - name: "MYPC GPU1 Information" value_template: "{{ value_json[1].index }}" json_attributes_path: "$.1" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature
-
platform: template sensors: mypc_gpu_0_gpu: friendly_name: "MYPC GPU0 GPU" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_memory: friendly_name: "MYPC GPU0 Memory" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_power: friendly_name: "MYPC GPU0 Power" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_0_power_limit: friendly_name: "MYPC GPU0 Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_0_temperature: friendly_name: "MYPC GPU0 Temperature" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'temperature') }}" unit_of_measurement: "C"
-
platform: template sensors: mypc_gpu_1_gpu: friendly_name: "MYPC GPU1 GPU" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_1_memory: friendly_name: "MYPC GPU1 Memory" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_1_power: friendly_name: "MYPC GPU1 Power" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_1_power_limit: friendly_name: "MYPC GPU1 Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_1_temperature: friendly_name: "MYPC GPU1 Temperature" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'temperature') }}" unit_of_measurement: "C"
```
Basic entity card:
type: entities entities: - entity: sensor.mypc_gpu_0_gpu secondary_info: last-updated - entity: sensor.mypc_gpu_0_memory secondary_info: last-updated - entity: sensor.mypc_gpu_0_power secondary_info: last-updated - entity: sensor.mypc_gpu_0_power_limit secondary_info: last-updated - entity: sensor.mypc_gpu_0_temperature secondary_info: last-updatedAnsible Role
```
-
name: install go become: true package: name: golang-go state: present
-
name: git clone git: repo: "https://github.com/sammcj/NVApi.git" dest: "/home/ansible/NVapi" update: yes force: true
go run main.go -port 9999 -rate 1
-
name: install systemd service become: true copy: src: nvapi.service dest: /etc/systemd/system/nvapi.service
-
name: Reload systemd daemons, enable, and restart nvapi become: true systemd: name: nvapi daemon_reload: yes enabled: yes state: restarted ```
-
 @ f7a1599c:6f2484d5
2025-05-24 20:06:04
@ f7a1599c:6f2484d5
2025-05-24 20:06:04In March 2020, Lucas was afraid.
The economy was grinding to a halt. Markets were in freefall. In a sweeping response, the Federal Reserve launched an unprecedented intervention—buying everything from Treasury bonds and mortgages to corporate debt, expanding the money supply by $4 trillion. At the same time, the U.S. government issued over $800 billion in stimulus checks to households across the country.
These extraordinary measures may have averted a wave of business failures and bank runs—but they came at a cost: currency debasement and rising inflation. Alarmed by the scale of central bank intervention and its consequences for savers, Lucas decided to act.
In a state of mild panic, he withdrew $15,000 from his bank account and bought ten gold coins. Then he took another $10,000 and bought two bitcoins. If the dollar system failed, Lucas wanted something with intrinsic value he could use.
He mentioned his plan to his friend Daniel, who laughed.
“Why don’t you stock up on guns and cigarettes while you’re at it?” Daniel quipped. “The Fed is doing what it has to—stabilizing the economy in a crisis. Sure, $4 trillion is a lot of money, but it's backed by the most productive economy on Earth. Don’t panic. The world’s not ending.”
To prove his point, Daniel put $25,000 into the S&P 500—right at the pandemic bottom.
And he was right. Literally.
By Spring 2025, the stock market was near all-time highs. The world hadn’t ended. The U.S. economy kept moving, more or less as usual. Daniel’s investment had nearly tripled—his $25,000 had grown to $65,000.
But oddly enough, Lucas’ seemingly panicked reaction had been both prudent and profitable.
His gold coins had climbed from $1,500 to $3,300 apiece—a 120% gain. Bitcoin had soared from $5,000 to $90,000, making his two coins worth $180,000. Altogether, Lucas’s $25,000 allocation had grown to $213,000—a nearly 10x return. And his goal wasn’t even profit. It was safety.
With that kind of fortune, you’d expect Lucas to feel confident, even serene. He had more than enough to preserve his purchasing power, even in the face of years of inflation.
But in the spring of 2025, Lucas felt anything but calm.
He was uneasy—gripped by a sense that the 2020 crisis hadn’t been a conclusion, but a prelude.
In his mind, 2020 was just the latest chapter in a troubling sequence: the Asian financial crisis in 1998, the global financial crisis in 2008, the pandemic shock of 2020. Each crisis had been more sudden, more sweeping, and more dependent on emergency measures than the last.
And Lucas couldn’t shake the feeling that the next act—whenever it came—would be more disruptive, more severe, and far more damaging.
-
 @ 21335073:a244b1ad
2025-03-18 14:43:08
@ 21335073:a244b1ad
2025-03-18 14:43:08Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ 47259076:570c98c4
2025-05-25 01:33:57
@ 47259076:570c98c4
2025-05-25 01:33:57When a man meets a woman, they produce another human being.
The biological purpose of life is to reproduce, that's why we have reproductive organs.
However, you can't reproduce if you are dying of starvation or something else.
So you must look for food, shelter and other basic needs.
Once those needs are satisfied, the situation as a whole is more stable and then it is easier to reproduce.
Once another human being is created, you still must support him.
In the animal kingdom, human babies are the ones who take longer to walk and be independent as a whole.
Therefore, in the first years of our lives, we are very dependent on our parents or whoever is taking care of us.
We also have a biological drive for living.
That's why when someone is drowning he will hold on into whatever they can grab with the highest strength possible.
Or when our hand is close to fire or something hot, we remove our hand immediately from the hot thing, without thinking about removing our hand, we just do it.
These are just 2 examples, there are many other examples that show this biological tendency/reflex to keep ourselves alive.
We also have our brain, which we can use to get information/knowledge/ideas/advice from the ether.
In this sense, our brain is just an antenna or radio, and the ether is the signal.
Of course, we are not the radio, we are the signal.
In other words, you are not your body, you are pure consciousness "locked" temporarily in a body.
Because we can act after receiving information from the ether, we can construct and invent new things to make our lives easier.
So far, using only biology as our rule, we can get to the following conclusion: The purpose of life is to live in a safe place, work to get food and reproduce.
Because humans have been evolving in the technological sense, we don't need to hunt for food, we can just go to the market and buy meat.
And for the shelter(house), we just buy it.
Even though you can buy a house, it's still not yours, since the government or any thug can take it from you, but this is a topic for another article.
So, adjusting what I said before in a modern sense, the purpose of life is: Work in a normal job from Monday to Friday, save money, buy a house, buy a car, get a wife and have kids. Keep working until you are old enough, then retire and do nothing for the rest of your life, just waiting for the moment you die.
Happy life, happy ending, right?
No.
There is something else to it, there is another side of the coin.
This is explored briefly by Steve Jobs in this video, but I pretend to go much further than him: https://youtu.be/uf6TzOHO_dk
Let's get to the point now.
First of all, you are alive. This is not normal.
Don't take life for granted.
There is no such a thing as a coincidence. Chance is but a name given for a law that has not been recognized yet.
You are here for a reason.
God is real. All creation starts in the mind.
The mind is the source of all creation.
When the mind of god starts thinking, it records its thoughts into matter through light.
But this is too abstract, let's get to something simple.
Governments exist, correct?
The force behind thinking is desire, without desire there is no creation.
If desired ceased to exist, everything would just vanish in the blink of an eye.
How governments are supported financially?
By taking your money.
Which means, you produce, and they take it.
And you can't go against it without suffering, therefore, you are a slave.
Are you realizing the gravity of the situation?
You are working to keep yourself alive as well as faceless useless men that you don't even know.
Your car must have an identification.
When you are born, you must have an identification.
In brazil, you can't home school your children.
When "your" "country" is in war, you must fight to defend it and give your life.
Countries are limited by imaginary lines.
How many lives have been destroyed in meaningless wars?
You must go to the front-line to defend your masters.
In most countries, you don't have freedom of speech, which means, you can't even express what you think.
When you create a company, you must have an identification and pass through a very bureaucratic process.
The money you use is just imaginary numbers in the screen of a computer or phone.
The money you use is created out of thin air.
By money here, I am referring to fiat money, not bitcoin.
Bitcoin is an alternative to achieve freedom, but this is topic for another article.
Depending on what you want to work on, you must go to college.
If you want to become a doctor, you must spend at least 5 years in an university decorating useless muscle names and bones.
Wisdom is way more important than knowledge.
That's why medical errors are the third leading cause of death in United States of America.
And I'm not even talking about Big Pharma and the "World Health Organization"
You can't even use or sell drugs, your masters don't allow it.
All the money you get, you must explain from where you got it.
Meanwhile, your masters have "black budget" and don't need to explain anything to you, even though everything they do is financed by your money.
In most countries you can't buy a gun, while your masters have a whole army fully armed to the teeth to defend them.
Your masters want to keep you sedated and asleep.
Look at all the "modern" art produced nowadays.
Look at the media, which of course was never created to "inform you".
Your masters even use your body to test their bio-technology, as happened with the covid 19 vaccines.
This is public human testing, there's of course secretive human testing, such as MKUltra and current experiments that happen nowadays that I don't even know.
I can give hundreds of millions of examples, quite literally, but let's just focus in one case, Jeffrey Epstein.
He was a guy who got rich "suddenly" and used his influence and spy skills to blackmail politicians and celebrities through recording them doing acts of pedophilia.
In United States of America, close to one million children a year go missing every year.
Some portion of these children are used in satanic rituals, and the participants of these rituals are individuals from the "high society".
Jeffrey Epstein was just an "employee", he was not the one at the top of the evil hierarchy.
He was serving someone or a group of people that I don't know who they are.
That's why they murdered him.
Why am I saying all of this?
The average person who sleep, work, eat and repeat has no idea all of this is going on.
They have no idea there is a very small group of powerful people who are responsible for many evil damage in the world.
They think the world is resumed in their little routine.
They think their routine is all there is to it.
They don't know how big the world truly is, in both a good and evil sense.
Given how much we produce and all the technology we have, people shouldn't even have to work, things would be almost nearly free.
Why aren't they?
Because of taxes.
This group of people even has access to a free energy device, which would disrupt the world in a magnitude greater than everything we have ever seen in the history of Earth.
That's why MANY people who tried to work in any manifestation of a free energy device have been murdered, or rather, "fell from a window".
How do I know a free energy device exist? This is topic for another article.
So my conclusion is:
We are in hell already. Know thyself. Use your mind for creation, any sort of creation. Do good for the people around you and the people you meet, always give more than you get, try to do your best in everything you set out to do, even if it's a boring or mundane work.
Life is short.
Our body can live no longer than 300 years.
Most people die before 90.
Know thyself, do good to the world while you can.
Wake up!!! Stop being sedated and asleep.
Be conscious.
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 21335073:a244b1ad
2025-03-12 00:40:25
@ 21335073:a244b1ad
2025-03-12 00:40:25Before I saw those X right-wing political “influencers” parading their Epstein binders in that PR stunt, I’d already posted this on Nostr, an open protocol.
“Today, the world’s attention will likely fixate on Epstein, governmental failures in addressing horrific abuse cases, and the influential figures who perpetrate such acts—yet few will center the victims and survivors in the conversation. The survivors of Epstein went to law enforcement and very little happened. The survivors tried to speak to the corporate press and the corporate press knowingly covered for him. In situations like these social media can serve as one of the only ways for a survivor’s voice to be heard.
It’s becoming increasingly evident that the line between centralized corporate social media and the state is razor-thin, if it exists at all. Time and again, the state shields powerful abusers when it’s politically expedient to do so. In this climate, a survivor attempting to expose someone like Epstein on a corporate tech platform faces an uphill battle—there’s no assurance their voice would even break through. Their story wouldn’t truly belong to them; it’d be at the mercy of the platform, subject to deletion at a whim. Nostr, though, offers a lifeline—a censorship-resistant space where survivors can share their truths, no matter how untouchable the abuser might seem. A survivor could remain anonymous here if they took enough steps.
Nostr holds real promise for amplifying survivor voices. And if you’re here daily, tossing out memes, take heart: you’re helping build a foundation for those who desperately need to be heard.“
That post is untouchable—no CEO, company, employee, or government can delete it. Even if I wanted to, I couldn’t take it down myself. The post will outlive me on the protocol.
The cozy alliance between the state and corporate social media hit me hard during that right-wing X “influencer” PR stunt. Elon owns X. Elon’s a special government employee. X pays those influencers to post. We don’t know who else pays them to post. Those influencers are spurred on by both the government and X to manage the Epstein case narrative. It wasn’t survivors standing there, grinning for photos—it was paid influencers, gatekeepers orchestrating yet another chance to re-exploit the already exploited.
The bond between the state and corporate social media is tight. If the other Epsteins out there are ever to be unmasked, I wouldn’t bet on a survivor’s story staying safe with a corporate tech platform, the government, any social media influencer, or mainstream journalist. Right now, only a protocol can hand survivors the power to truly own their narrative.
I don’t have anything against Elon—I’ve actually been a big supporter. I’m just stating it as I see it. X isn’t censorship resistant and they have an algorithm that they choose not the user. Corporate tech platforms like X can be a better fit for some survivors. X has safety tools and content moderation, making it a solid option for certain individuals. Grok can be a big help for survivors looking for resources or support! As a survivor, you know what works best for you, and safety should always come first—keep that front and center.
That said, a protocol is a game-changer for cases where the powerful are likely to censor. During China's # MeToo movement, survivors faced heavy censorship on social media platforms like Weibo and WeChat, where posts about sexual harassment were quickly removed, and hashtags like # MeToo or "woyeshi" were blocked by government and platform filters. To bypass this, activists turned to blockchain technology encoding their stories—like Yue Xin’s open letter about a Peking University case—into transaction metadata. This made the information tamper-proof and publicly accessible, resisting censorship since blockchain data can’t be easily altered or deleted.
I posted this on X 2/28/25. I wanted to try my first long post on a nostr client. The Epstein cover up is ongoing so it’s still relevant, unfortunately.
If you are a survivor or loved one who is reading this and needs support please reach out to: National Sexual Assault Hotline 24/7 https://rainn.org/
Hours: Available 24 hours
-
 @ 502ab02a:a2860397
2025-05-25 01:03:51
@ 502ab02a:a2860397
2025-05-25 01:03:51บางครั้งพลังยิ่งใหญ่ที่สุดก็ไม่ใช่สิ่งที่เห็นได้ด้วยตาเปล่า เหมือนแสงแดดที่คนส่วนใหญ่มักจะกลัวเพราะกลัวผิวเสีย กลัวฝ้า กลัวร้อน แต่แท้จริงแล้วในแสงแดดมีบางสิ่งที่น่าเคารพอยู่ลึกๆ มันคือแสงที่มองไม่เห็น มันไม่แสบตา ไม่แสบผิว แต่มันลึก ถึงเซลล์ มันคือ “แสงอินฟราเรด” ที่ซ่อนตัวอย่างสุภาพในแดดยามเช้า
เฮียมักชอบพูดว่า แดดที่ดีไม่จำเป็นต้องแสบหลัง อาบแสงที่ลอดผ่านใบไม้ยามเช้าแบบไม่ต้องฝืนตาก็พอ แสงอินฟราเรดนี่แหละคือพระเอกตัวจริงในความเงียบ มันไม่ดัง ไม่โชว์ ไม่โฆษณา แต่มันลงลึกไปถึงระดับที่ร่างกายเรากำลังหิวโดยไม่รู้ตัวในระดับเซลล์
ในเซลล์ของเรา มีหน่วยผลิตพลังงานที่เรียกว่าไมโทคอนเดรีย เจ้านี่แหละคือโรงไฟฟ้าจิ๋วประจำบ้าน ที่ต้องตื่นมาทำงานทุกวันโดยไม่ได้หยุดเสาร์อาทิตย์ ยิ่งถ้าไมโทคอนเดรียทำงานไม่ดี ร่างกายก็จะเหมือนไฟตกทั้งระบบ—ง่วงง่าย เพลียไว ปวดนู่นปวดนี่เหมือนไฟในบ้านกระพริบตลอดเวลา
แล้วแสงอินฟราเรดเกี่ยวอะไรกับมัน? เฮียขอเล่าง่ายๆ ว่า ไมโทคอนเดรียมีตัวรับแสงตัวหนึ่งชื่อว่า cytochrome c oxidase เจ้านี่ตอบสนองต่อแสงอินฟราเรดช่วงคลื่นเฉพาะ คือประมาณ 600–900 นาโนเมตร พอโดนเข้าไป มันเหมือนได้จุดประกายให้โรงงานพลังงานในร่างกายกลับมาคึกคักอีกครั้ง ผลิตพลังงานได้มากขึ้น ระบบไหลเวียนเลือดก็ดีขึ้น เหมือนท่อน้ำที่เคยอุดตันก็กลับมาใสแจ๋ว ความอักเสบเล็กๆ ในร่างกายก็ลดลง คล้ายบ้านที่เคยอับชื้นแล้วได้เปิดหน้าต่างให้แสงแดดส่องเข้าไป
และที่น่ารักกว่านั้นคือ เราไม่ต้องไปถึงชายหาด ไม่ต้องจองรีสอร์ตริมทะเล แค่แดดเช้าอ่อนๆ ข้างบ้านหรือตามขอบระเบียง ก็ให้แสงอินฟราเรดได้แล้ว ถ้าใครอยู่ในเมืองใหญ่ที่มีแต่ตึกบังแดด แล้วจะเลือกใช้หลอดไฟ Red Light Therapy ก็ไม่ผิด แต่ต้องเลือกแบบรู้เท่าทันรู้ ไม่ใช่เห็นใครรีวิวก็ซื้อมาเปิดใส่หน้า หวังจะหน้าใสข้ามคืน ต้องเข้าใจทั้งความยาวคลื่น เวลาใช้งาน และจุดประสงค์ ไม่ใช่ใช้เพราะแค่กลัวแก่อยากหน้าตึง แต่ใช้เพราะอยากให้ร่างกายกลับไปทำงานอย่างเป็นธรรมชาติอีกครั้ง และอยู่ในประเทศหรือสถานที่ที่โดนแดดได้น้อยอยากได้เสริมเฉยๆ
แล้วเราจะรู้ได้ยังไงว่าไมโทคอนเดรียเรากลับมาทำงานดีขึ้น? เฮียว่าไม่ต้องรอผลเลือดจากแล็บไหนก็รู้ได้ อย่าไปยึดติดกับตัวเลขมากครับ เอาตัวเองเป็นหลัก ตั้งคำถามกับตัวเองว่ารู้สึกยังไงบ้าง ถ้าเริ่มนอนหลับลึกขึ้น ตื่นมาแล้วหัวไม่มึน ไม่หงุดหงิดตั้งแต่ยังไม่ลืมตา ถ้าปวดหลังปวดข้อที่เคยมีเริ่มหายไปแบบไม่ได้กินยา หรือแม้แต่ผิวที่ดูสดใสขึ้นแบบไม่ต้องง้อสกินแคร์ นั่นแหละคือเสียงขอบคุณเบาๆ จากไมโทคอนเดรียที่ได้แสงแดดแล้วกลับมามีชีวิตอีกครั้ง ถ้ามันดีก็คือดี
บางที เราไม่ต้องกินวิตามินเม็ดไหนเพิ่ม แค่เดินออกไปรับแดดเบาๆ ในเวลาเช้าๆ แล้วให้ร่างกายได้พูดคุยกับธรรมชาติบ้าง เพราะในความอบอุ่นเงียบๆ ของแสงอินฟราเรดนั้น มีเสียงเบาๆ ที่กำลังปลุกพลังในตัวเราให้กลับมาอีกครั้ง
แดดไม่ใช่ศัตรู ถ้าเรารู้จักมันในมุมที่ถูกต้อง เฮียแค่อยากชวนให้ลองเปลี่ยนจากคำว่า “กลัวแดด” เป็น “ฟังแดด” เพราะบางครั้งธรรมชาติไม่ได้พูดด้วยคำ แต่สื่อสารด้วยแสงที่แทรกผ่านหัวใจเราโดยไม่ต้องผ่านล่าม
บางคนอาจคิดในใจ “แหมเฮีย ก็ดีหรอก ถ้าได้ตื่นเช้า” 555555
เฮียเข้าใจดีเลยว่าไม่ใช่ทุกคนจะตื่นมาทันแดดยามเช้าได้เสมอไป ชีวิตคนเรามันไม่ได้เริ่มต้นพร้อมไก่ขันทุกวัน บางคนเพิ่งเข้านอนตอนตีสาม ตื่นอีกทีแดดก็แตะบ่ายเข้าไปแล้ว ไม่ต้องกังวลไปจ้ะ เพราะความมหัศจรรย์ของแสงอินฟราเรดยังมีให้เราได้ใช้แม้ในแดดยามเย็น
แดดช่วงเย็น โดยเฉพาะหลังสี่โมงเย็นไปจนเกือบหกโมง (หรือเร็วช้าตามฤดู) ก็ยังอุดมไปด้วยแสงอินฟราเรดในช่วงคลื่นที่ไมโทคอนเดรียชอบ แถมยังไม่มีรังสี UV ที่แรงจัดมารบกวนเหมือนตอนเที่ยง เรียกว่าเป็นแดดแบบละมุนๆ สำหรับคนที่อยาก “บำบัดใจ” แบบไม่ต้องร้อนจนหัวเปียก
เฮียเคยลองตากแดดเย็นเดินไปในสวนสาธารณะ แล้วรู้สึกว่ามันเหมือนได้รีเซ็ตจิตใจหลังวันเหนื่อยๆ ไปในตัว ยิ่งพอรู้ว่าในช่วงเวลานี้แสงที่ได้กำลังช่วยปลุกพลังงานในร่างกายแบบเงียบๆ ด้วยแล้ว มันทำให้เฮียยิ่งเคารพธรรมชาติมากขึ้นไปอีก เคยเห็นคนที่วันๆมีแต่ความเครียด ความโกรธ ความอาฆาตต่อโลกไหมหละ บางคนแค่โดนแดด แต่ไม่ได้ตากแดด การตากแดดคือปล่อยใจไปกับธรรมชาติ พูดคุยกับร่างกาย บอกเขาว่าเราจะทำตัวให้เป็นประโยชน์กับโลกใบนี้ ให้สมกับที่ใช้พลังงานของโลก
จะเช้าหรือเย็น สำคัญไม่เท่ากับความตั้งใจ เฮียว่าไม่ว่าชีวิตจะตื่นตอนไหน ถ้าเราให้เวลาแค่ 10–15 นาทีในแต่ละวัน ออกไปยืนให้แดดแตะหน้า แตะแขน หรือแค่ให้แสงลอดผ่านตาเบาๆ โดยไม่ต้องจ้องจ้าๆ ก็พอ แค่นี้ก็เป็นการให้ไมโทคอนเดรียได้หายใจ ได้ออกกำลังกายแบบของมัน และได้ส่งพลังกลับมาหาเราทั้งร่างกายและจิตใจ
สุดท้ายแล้ว แดดไม่ได้แบ่งชนชั้น ไม่เลือกว่าจะรักเฉพาะคนตื่นเช้า หรือโกรธคนตื่นสาย ขอแค่เรารู้จักเวลาและวิธีอยู่กับมันอย่างถูกจังหวะ แดดก็พร้อมจะให้เสมอ
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr #SundaySpecialเราจะไปเป็นหมูแดดเดียว
-
 @ 15cf81d4:b328e146
2025-05-24 19:19:46
@ 15cf81d4:b328e146
2025-05-24 19:19:46Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ 47c860d3:b3f71b74
2025-05-25 01:56:39
@ 47c860d3:b3f71b74
2025-05-25 01:56:39ไขความลับรหัส 13 ตัวอักษรของ FT8: ศาสตร์แห่งการบีบอัดข้อมูลสื่อสารดิจิทัล คืนหนึ่ง ผมนั่งอยู่หน้าจอคอมพิวเตอร์ มองสัญญาณ FT8 กระพริบไปมา ส่งข้อความสั้นๆ ซ้ำไปซ้ำมา "CQ HS1IWX OK03" แล้วก็รอให้ใครสักคนตอบกลับ วนลูปไปอย่างไม่รู้จบ จนเกิดคำถามขึ้นมาในหัว... “นี่เรานั่งทำอะไรกันแน่?” FT8 มันควรเป็นอะไรมากกว่านี้ใช่ไหม? ไม่ใช่แค่การส่งคำสั้นๆ 13 ตัวอักษรไปมาเท่านั้น! เอ๊ะ! เดี๋ยวก่อน... 13 ตัวอักษร? ถ้าการส่งข้อความจำกัดที่ 13 ตัวอักษร แล้วทำไมข้อความอย่าง "CQ HS1IWX OK03" ซึ่งดูเหมือนจะมี 14 ตัวอักษร (รวมช่องว่าง) ถึงสามารถส่งได้? นี่มันต้องมีอะไรซ่อนอยู่! ระบบ FT8 ใช้เวทมนตร์อะไร หรือมันมีเทคนิคการเข้ารหัสแบบลับๆ ที่เรายังไม่รู้? และคำว่า "13 ตัวอักษร" ที่เขาพูดถึงนั้นหมายถึงอะไรกันแน่? แล้วลองนึกดูสิ... ถ้าเราอยู่ในสถานการณ์ฉุกเฉิน ต้องส่งข้อความที่สั้น กระชับ และมีความหมาย ในขณะที่แบตเตอรี่เหลือน้อย กำลังส่งต่ำ และอุปกรณ์มีเพียงเครื่องวิทยุขนาดเล็กกับสายอากาศชั่วคราวและมือถือ บางครั้ง FT8 อาจจะเป็นตัวเลือกเดียวที่ช่วยให้เราส่งสัญญาณขอความช่วยเหลือได้ เพราะมันสามารถถอดรหัสได้แม้สัญญาณอ่อนจนแทบจะมองไม่เห็น! ดังนั้น ผมต้องขุดลึกลงไป เพื่อไขความลับของรหัส 13 ตัวอักษรของ FT8 และหาคำตอบว่า ทำไม FT8 สามารถส่งข้อความบางอย่างที่ดูเหมือนยาวเกินขีดจำกัดได้? พร้อมกับสำรวจว่ามันสามารถช่วยเหลือเราในสถานการณ์ฉุกเฉินได้อย่างไร! อะไรคือความหมายที่แท้จริงของ 13 ตัวอักษร ? เมื่อเริ่มเจาะลึกลงไป ผมจึงได้รู้ว่า 13 ตัวอักษรที่เราพูดถึงนั้นหมายถึง ข้อความใน Free Text Mode หรือก็คือ ข้อความที่ไม่ได้ถูกเข้ารหัสในรูปแบบมาตรฐานของ FT8 หากเราส่งข้อความแบบอิสระ เช่น "HELLO WORLD!" หรือ "EMERGENCY CALL" เราจะถูกจำกัดแค่ 13 ตัวอักษรเท่านั้น เพราะข้อความเหล่านี้ไม่ได้ถูกเข้ารหัสให้เหมาะสมกับโปรโตคอลของระบบ FT8 แต่ถ้าเป็น ข้อความมาตรฐานที่ถูกกำหนดรูปแบบไว้แล้ว เช่น Callsign + Grid หรือ รายงาน SNR (-10, 599, RR73) ระบบ FT8 จะใช้การเข้ารหัส 77-bit Structured Message ซึ่งช่วยให้สามารถส่งข้อมูลได้มากกว่า 13 ตัวอักษร! อะไรคือ โครงสร้าง 77-bit Message ใน FT8 FT8 ใช้ 77 บิต สำหรับการเข้ารหัสข้อมูล โดยแบ่งออกเป็น 3 ส่วนหลัก: ส่วนของข้อมูล จำนวนบิต รายละเอียด Callsign 1 (ต้นทาง) 28 บิต รหัสสถานีที่ส่ง Callsign 2 (ปลายทาง) 28 บิต รหัสสถานีปลายทาง หรือ CQ Exchange Data 21 บิต Grid Locator หรือข้อมูลอื่น ๆ รวมทั้งหมด = 28 + 28 + 21 = 77 บิต การที่ FT8 ใช้โครงสร้างแบบนี้ ข้อความที่ถูกเข้ารหัสในมาตรฐาน FT8 จึงสามารถส่งได้มากกว่า 13 ตัวอักษร เช่น "CQ HS1IWX OK03" นั้นถูกเข้ารหัสให้อยู่ใน 77 บิต ไม่ใช่ Free Text แบบปกติ ทำให้สามารถส่งได้โดยไม่มีปัญหา! แต่ข้อสำคัญมันคือโปโตคอลของระบบ FT8 ในปัจจุบัน ถ้าเราต้องการ เข้ารหัสเองในรูปแบบของเราเราก็ต้องพัฒนาโปรแกรม FT8 ของเราเอง (ผมทำไม่เป็นครับ555) ก็ใช้ของเขาไปก็ได้ แล้วก็มาพัฒนาระบบ เทคนิคการส่งข้อมูลให้มีประสิทธิภาพภายใน 13 ตัวอักษร กันน่าจะสนุกกว่า ส่วนเรื่องรายละเอียดวิธีการเข้ารหัสผมคงไม่พูดถึงนะ เดี๋ยวจะวิชาการน่าเบื่อไปครับ ใครสนใจก็ไปศึกษาต่อกันเอาเองครับ การเข้ารหัสนี้จะใช้ร่วมกับเทคนิค FEC (Forward Error Correction) ใน FT8 ซึ่งเป็นหนึ่งในเทคนิคที่ทำให้ FT8 สามารถถอดรหัสข้อความได้แม้ในสภาวะสัญญาณอ่อน คือการใช้ Forward Error Correction (FEC) หรือ การแก้ไขข้อผิดพลาดล่วงหน้า ซึ่งช่วยให้สามารถกู้คืนข้อมูลที่อาจเกิดการสูญหายในระหว่างการส่งสัญญาณได้ โดย FT8 ใช้ Reed-Solomon (RS) Error Correction Code ซึ่งเป็นอัลกอริธึมที่เพิ่มบิตสำรองเพื่อช่วยตรวจจับและแก้ไขข้อผิดพลาดในข้อความที่ส่งไป และ ใช้ Convolutional Encoding และ Viterbi Decoding ซึ่งช่วยให้สามารถแก้ไขข้อมูลที่ผิดพลาดจากสัญญาณรบกวนได้ ซึ่งเมื่อสัญญาณอ่อน ข้อมูลบางส่วนอาจสูญหาย แต่ FEC ช่วยให้สามารถกู้คืนข้อความได้แม้ข้อมูลบางส่วนจะขาดหาย ทำให้ผลลัพธ์คือ FT8 สามารถทำงานได้แม้ระดับสัญญาณต่ำถึง -20 dB! ซึ่งส่วนนี้ผมก็ยังไม่เข้าใจมันดีเท่าไหร่ครับ อิอิ ฟังเขามาอีกที สิ่งที่เราทำได้ตอนนี้ในโปรแกรม FT8 ในปัจจุบันก็คือ เทคนิคการส่งข้อมูลให้มีประสิทธิภาพภายใน 13 ตัวอักษรถ้าเรา อยากส่งข้อความฉุกเฉินภายใน 13 ตัวอักษร ให้ได้ข้อมูลมากที่สุด เราต้องใช้เทคนิคต่อไปนี้: การใช้ตัวย่อและรหัสสากล • SOS 1234 BKK แทน "ขอความช่วยเหลือที่พิกัด 1234 ใกล้กรุงเทพ" • WX BKK T35C แทน "สภาพอากาศกรุงเทพ 35 องศา" • ALRT TSUNAMI แทน "เตือนภัยสึนามิ" ใช้ข้อความที่อ่านเข้าใจง่าย • ใช้โค้ดสั้นๆ เช่น "QRZ EMRG?" แทน "ใครรับสัญญาณฉุกเฉิน?" การส่งข้อความเป็นชุด • เฟรม 1: MSG1 BKK STORM1 • เฟรม 2: MSG2 BKK STORM2 • เฟรม 3: MSG3 BKK NOW “การฝึกฝนเพื่อทำความเข้าใจการสื่อสารเป็นสิ่งสำคัญ เพราะเมื่อได้รับข้อความเหล่านี้ เราจะสามารถถอดรหัสและติดตามข้อมูลได้อย่างทันท่วงที” ครั้งนี้อาจเป็นเพียงการค้นพบอีกด้านหนึ่งของ FT8… หรือมันอาจเปลี่ยนมุมมองของคุณที่มีต่อโหมดสื่อสารดิจิทัลไปตลอดกาลก็ได้ แต่เดี๋ยวก่อน—นี่มันอะไรกัน!? จู่ๆ บนจอคอมพิวเตอร์ของผมก็ปรากฏคอลซายที่ไม่คุ้นตา D1IFU—คอลซายที่ไม่มีอยู่ในฐานข้อมูลของ ITU แต่กลับปรากฏขึ้นบนคลื่นความถี่ของเรา D1…? มันมาได้ยังไง? แล้วทันใดนั้น ผมก็ฉุกคิดขึ้นมา—มันคือคอลซายจากพื้นที่ Donetsk หรือ Luhansk พื้นที่ที่เต็มไปด้วยความขัดแย้ง ดินแดนที่เราคิดว่าเงียบงันภายใต้เสียงระเบิดและความไม่แน่นอน แต่ตอนนี้ กลับมีสัญญาณเล็กๆ ปรากฏขึ้นบน FT8 มันคือใครกัน? เป็นทหาร? เป็นพลเรือนที่พยายามติดต่อโลกภายนอก? หรือเป็นเพียงนักวิทยุสมัครเล่นที่ยังคงเฝ้าฟังแม้โลกจะเต็มไปด้วยความวุ่นวาย? แต่สิ่งหนึ่งที่แน่ชัด… “นี่คือสัญญาณแห่งชีวิต” จบข่าว. 🚀📡
-
 @ 3283ef81:0a531a33
2025-05-24 18:41:43
@ 3283ef81:0a531a33
2025-05-24 18:41:43Why
is
this
noton
separate
lines -
 @ 04c915da:3dfbecc9
2025-03-10 23:31:30
@ 04c915da:3dfbecc9
2025-03-10 23:31:30Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Usually stolen bitcoin for the reserve creates a perverse incentive. If governments see a bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 866e0139:6a9334e5
2025-05-22 06:46:34
@ 866e0139:6a9334e5
2025-05-22 06:46:34Autor: Jana Moava. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie auch in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Zwei Worte nur braucht man – und die Sache ist klar. Jeder gebildete Russe kennt diese Worte: sie stammen aus dem XIX. Jahrhundert, als Nikolaus I. die Krim-Kampagne begann und das Zarenreich nach üblen Querelen ganz Europa und die Türkei zum Gegner hatte - allen voran die Herrscher der Weltmeere: das British Empire mit Queen Victoria. Der historische Ausdruck anglitschanka gadit (locker übersetzt: die Engländerin macht Shit) besitzt bis heute verdeckte politische Sprengkraft und ist seit Ende Februar 2022 in Russland wieder populär. Wer auch immer der Urheber dieser im Original durchaus diskreten Benennung des Fäkalvorgangs war: der Ausdruck steht für ernste Konflikte mit dem Englisch sprechenden Westen, dem Erzfeind.
Ein kurzer Blick in die Geschichte mag dies erläutern: Fast alle westlichen Historiker benennen als Auslöser des Krimkrieges Mitte des IX. Jahrhunderts die Verteidigung der russisch-orthodoxen Kirche und deren Zugang zur Kreuzkirche in Jerusalem. Es wird vom letzten Kreuzzug u.a. geschrieben. Das ist eine höchst einseitige Interpretation, denn es ging Nikolaus I. vor allem um den Zugang zum einzigen dauerhaft eisfreien Hafen Russlands im Schwarzen Meer, durch die Meeresenge der Dardanellen ins Mittelmeer. Das ist verständlich, war doch die Eroberung der Krim ab 1783 unter seiner Großmutter Katharina II. aus eben diesem Grunde erfolgt. Damals schon wurde der Hafen Sewastopol zum Stützpunkt der russischen Flotte ausgebaut.
Ende 1825, nach dem plötzlichen Tod des ältesten Bruders Alexander I., war Nikolaus von seiner Erziehung her auf eine Regentschaft ganz und gar nicht vorbereitet gewesen, doch herrschte er dreißig Jahre lang nicht nur über das russische Reich, sondern auch über Finnland und das damalige Königreich Polen unter russischem Protektorat. Nikolaus I. zeichnete sich von Beginn an durch Gewaltmaßnahmen aus: Als ihm im Dezember (russ. dekabr)1825 eine Gruppe sehr gebildeter, freiheitsliebender junger Adligen aus besten Familien den Eid verweigerte (dies zog als Dekabristenaufstand in die Geschichte ein), ließ er fünf der Rebellen hängen, die anderen schickte er in Fußfesseln nach Sibirien in die Bergwerke. Er gründete die berüchtigte Geheimpolizei Dritte Abteilung, ließ Privatbriefe des Dichters Puschkin öffnen (obwohl dieser „in seiner Gnade stand“) und Historikern ist Nikolaus I. als Gendarm Europas bekannt. Im russischen Volk aber nannte man ihn kurz und bündig: *Nicki Knüppel aus dem Sack (Nikolaschka palkin). *
Leo Tolstoj beschrieb diesen Zaren in seinen Erzählungen über die Kriege im Kaukasus (Hadschi Murat) als feist und fett, mit leblosen, trüben Augen und als berüchtigten Frauenjäger. Tolstoj war es auch, der als junger Teilnehmer im Krimkrieg drei Erzählungen schrieb: Sewastopol im Dezember 1854, im Mai 1855 und im August 1855. Nachdem das British Empire unter Queen Victoria Russland den Krieg erklärt hatte (in Koalition mit Frankreich und Piemont-Sardinien als Schutzmacht des Osmanischen Reiches), entstand der Ausdruck anglitschanka gadit – die Engländerin macht Shit. Bis heute findet man dazu drastische Illustrationen im Netz…
Noch bevor russische Truppen Ende Februar 2022 in die Ukraine marschierten, lebte dieser Ausdruck in Russland wieder auf. Wer hierzulande Interesse an der Wahrheit hat, kann deutliche Parallelen zur damaligen politischen Lage entdecken, auch in Bezug auf die Verhaltensweisen des derzeitigen russischen Staatschefs und des historischen Nicki Knüppel aus dem Sack. Obwohl der amtierende durchaus Anerkennung verdient hat, denn nach dem Zusammenbruch der Sowjetunion in den 1990er Jahren unter Jelzin stellte er die Staatlich-keit des verlotterten, hungernden Landes wieder her und trieb den wirtschaftlichen Aufbau voran. Davon kann ich zeugen, lebte ich doch von 1992 – 2008 vor Ort.
Sicher - heute ist längst bekannt, daß die bereits Ende März 2022 in Istanbul laufenden Friedensverhandlungen zwischen Russland und der Ukraine vom britischen Premier und im Namen des US Präsidenten boykottiert wurden. Daniel Ruch, Schweizer Botschafter a.D., sprach gar von Sabotage! Der deutsche General a. D. Harald Kujat kommentierte damals mit den Worten: „Seit April 2022 gehen alle Kriegsopfer in der Ukraine auf das Konto des Westens!“ Der Ausdruck anglitschanka gadit ist seitdem in Russland wieder geläufig. Nun, brandaktuell, treffen sich die Kriegsparteien wieder in Istanbul: Ausgang ungewiss. Doch wird inzwischen auch von einzelnen westlichen Politikern anerkannt, dass Russland eine neutrale Pufferzone zu den Nato-Staaten verlangt und braucht.
Wenn hierzulande gemutmaßt wird, alle Russen würden den Ukraine-Krieg bejahen, so sollte man zur Kenntnis nehmen, dass derartige Aussagen kaum die wirkliche Überzeugung wiedergeben. Seit den Repressionen unter Stalin, seit in jeder zweiten Familie nahe Angehörige im GULAG einsaßen und umkamen und darüber Jahrzehnte lang geschwiegen werden musste, ist der Wahrheitsgehalt öffentlicher Umfragen getrost zu bezweifeln. Hat man hier etwa vergessen, dass seit 2011 auf eine mächtig wachsende zivile Protestbewegung und riesige Demonstrationen in russischen Großstädten immer schärfere Aktionen von Seiten des Staates erfolgten? Dass Knüppel auf Köpfe und Leiber prasselten, wie zur Zeit Nickis I., und der Polizeiapparat derart wuchs, dass heute das Verhältnis von Bürger und Silowiki (Vertreter der Gewalt)1:1 steht?
Offenbar weiß man hier nicht, dass schon Anfang 2022 von Mitarbeitern in jeder staatlich finanzierten Institution, ob im Bereich von Kultur, Wissenschaft, Forschung oder Lehre die schriftliche Zustimmung zur Spezialoperation mit der Ukraine eingefordert wurde! Eine Weigerung hatte den Verlust des Arbeitsplatzes zur Folge, egal welches Renommée oder welchen Rang der Betroffene besaß! Manche Leiter von staatlichen Institutionen zeigten dabei gehöriges Geschick und zeichneten für alle; andere (z.B. staatliche Theater) riefen jeden Mitarbeiter ins Kontor. Nur wenige Personen, die unter dem persönlichem Schutz des Präsidenten standen, konnten sich dieser Zustimmung zum Krieg entziehen. Wissenschaftler und Künstler emigrierten zuhauf. Berlin ist voll mit Geflohenen aus jenem Land, das kriegerisch ins Bruderland einmarschierte! Aber kann denn jeder emigrieren? Die Alten, Familien mit Kindern? Mit guten Freunden, die dort blieben, ist eine Kommunikation nur verschlüsselt möglich, in Nachrichten wie: die Feuer der Inquisition brennen (jeder, der von der offiziellen Doktrin abweicht, ist gefährdet), Ratten verbreiten Krankheiten bezieht sich auf Denunziationen, die in jeder Diktatur aufblühen, wenn sich jemand dem Schussfeld entziehen möchte und im vorauseilenden Gehorsam den Nachbarn anzeigt. Kennen wir das nicht noch aus unseren hitlerdeutschen 1930er Jahren?!
Je mehr im Reich aller Russen in den letzten Jahren von oben geknebelt und geknüppelt wurde, desto mehr Denunziationen griffen um sich. Junge Menschen, die auf Facebook gegen den Krieg posteten, wurden verhaftet. Seit 2023 sitzen u.a. zwei junge russische Theaterfrauen aufgrund der üblen Denunziation eines Kollegen hinter Gittern. Die Inszenierung der Regisseurin Zhenja Berkowitsch und der Autorin Swetlana Petritschuk erhielt Ende 2022 den höchsten Theaterpreis von ganz Russland, die Goldene Maske. Das Stück Finist (Phönix), klarer Falke ist nach dem Motiv eines russischen Märchens geschrieben, fußt aber auf dokumentarischem Material: es verhandelt die Versuchung junger Frauen, auf Islamisten hereinzufallen und sie aus Frust und falsch verstandener Solidarität zu heiraten. Die Anklage hat den Spieß genau umgedreht: Autorin und Regisseurin wurden des Terrorismus beschuldigt! Das Rechtssystem im Land scheint heute noch vergleichbar mit jenem, das Alexander Puschkin vor über 200 Jahren in seiner Erzählung Dubrowski authentisch beschrieb: Wer die Macht hat, regelt das Recht. Man kann die Erzählung des russischen Robin Hood auch deutsch nachlesen (leider, leider hat Puschkin sie nicht beendet).
Andere, erbaulichere Elemente aus der Zeit Puschkins, bzw. von Nikolaus I., dienen allerdings als Gegengewicht zum Alltag: seit Ende 2007 finden in Moskau und St. Petersburg jeden Winter nach dem Vorbild der historischen Adelsbälle große gesellschaftliche Events statt: Puschkinball, Wiener Opernball, jetzt nur noch Opernball genannt. Der Nachwuchs aus begüterten Familien lernt alte Tanzschritte und feine Sitten. Fort mit dem sowjetischen Schmuddelimage! Prächtige Kostümbälle werden nun zum Abschluss jedes Schuljahres aufgeboten. In stilisierten Kostümen der Zeit Nikolajs I. bzw. Puschkins tanzen Schuldirektoren, Lehrer und junge Absolventen. Der Drang nach altem Glanz und Größe (oder eine notwendige Kompensation?) spiegelt sich im Volk.
Werfen wir jedoch einen Blick auf einige Geschehnisse in der Ukraine ab 2014, die in unserer Presse immer noch verschwiegen werden: Im Spätsommer 2022 begegnete ich auf Kreta einer Ukrainerin aus der Nordukraine, die wegen des fürchterlichen Nationalismus nach 2014 ihre Heimat verließ. Sie ist nicht die einzige! Ihre Kinder waren erwachsen und zogen nach Polen, sie aber reiste mit einer Freundin weiter Richtung Griechenland, lernte die Sprache, erwarb die Staatsbürgerschaft und ist nun auf Kreta verheiratet.
Natalia erzählte mir, was bei uns kaum zu lesen ist, was jedoch Reporter wie Patrick Baab oder Historiker wie Daniele Ganser schon lange berichtet haben: 2014, als die Bilder der Proteste auf dem Maidan um die Welt gingen, habe die damalige amerikanische Regierung unter Präsident Biden die Vorgänge in Kiew für einen Putsch genutzt: Janukowitsch, der korrupte, doch demokratisch gewählte Präsident der Ukraine wurde gestürzt, die Ereignisse mit Hilfe von Strohmännern und rechten Nationalisten gelenkt, die mit Geld versorgt wurden. Bis es zum Massaker auf dem Maidan kam, als bewaffnete, ihrer Herkunft nach zunächst nicht identifi-zierbare Schützen (es waren v.a. rechte Nationalisten, so der gebürtige Ukrainer und US Bürger Professor N. Petro und Prof. Ivan Katchanovskij) von den Dächern in die Menge schossen.
Im YouTube Kanal Neutrality Studies konnte man am 17.02.2024 hören: Anlässlich des traurigen 10. Jahrestages des Maidan-Massakers, bei dem am 20. Februar 2014 mehr als 100 Menschen durch Scharfschützenfeuer getötet wurden, spreche ich heute mit Ivan Katchanovski, einem ukrainischen (und kanadischen) Politikwissenschaftler an der Univer-sität von Ottawa, der das Massaker detailliert erforscht hat. Letztes Jahr veröffentlichte er das Papier „Die Maidan-Massaker-Prozess und Untersuchungserkenntnisse: Implikationen für den Krieg zwischen der Ukraine und Russland und die Beziehungen“. Kurz gesagt, das Massaker wurde NICHT von den Kräften Victor Janukowytschs begangen, wie in westlichen Medien berichtet, und es gibt schlüssige Beweise dafür, dass die Schützen Teil des ultra-rechten Flügels der Ukraine waren, die dann nach dem Putsch an die Macht kamen. (Link zum Paper).
Wer erinnert sich hierzulande noch daran, dass 2014 im deutschen öffentlichen Fernsehen von Hunter Biden, Sohn des US-Präsidenten berichtet wurde, der durch dubiose Gas- und Ölgeschäfte in der Ukraine auffiel? Dass damals im deutschen Fernsehen auch Bilder von Ukrainern mit SS-Stahlhelmen auftauchten? In einer Arte-Reportage zu Hilfs-transporten im März 2022 aus Polen über die Westukraine konnte der aufmerksame Zu-schauer an fast allen Häusern die tiefroten Banner von Anhängern des verstorbenen, in München begrabenen, faschistischen Stepan Bandera erkennen. Ausgesprochen wurde es nicht.
Die neue Kreterin Natalia sprach auch über eine Amerikanerin ukrainischer Herkunft, die Röntgenärztin Uljana Suprun, die aus den USA als Gesundheitsministerin rekrutiert wurde und unter dem amerikafreundlichen Präsidenten Poroschenko von 2016-2019 diesen Posten innehatte. Was bitte sollte eine Röntgenärztin aus den USA auf dem Ministerposten der Ukraine?! Streit und Skandal umgaben sie fast täglich in der RADA, dem ukrainischen Parlament. Es wurde gemunkelt, sie diene als Feigenblatt bei der Herstellung biologischer Waffen. Material zu ihr ist bis heute auf YouTube zu finden.
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes.
Natalia bezeichnete die ukrainischen Emigrantenkreise in den USA und Kanada zurecht als ultranationalistisch, sie seien Kollaborateure der Nazis bei der Judenvernichtung gewesen und hätten sich nach dem Rückzug der Deutschen rechtzeitig nach Übersee abgesetzt. Das ist wohl bekannt.
Heute ist das Recherchieren der wahren Geschehnisse von 2014 zwar immer noch mühsam, aber die Wahrheit sickert immer mehr durch, zumal auch Exilukrainer dazu geschrieben und öffentlich gesprochen haben. Die Kanäle SaneVox und Neutrality studies liefern unermüdlich weitere Fakten! Im März 2025 klärte der US-Professor Jeffrey Sachs das Europa-Parlament endlich in allen Details über die kriegerischen Machenschaften bestimmter Kreise innerhalb der englischsprechenden Westmächte auf!
Kürzlich war im multipolar-magazin zu lesen, wie erschreckend tief unser eigenes Land bereits in**** den Ukraine-Krieg verwickelt ist: Da hieß es:
*„Kriegsplanung von deutschem Boden“ *
Zwei umfassende Beiträge der „New York Times“ und der Londoner „Times“ belegen, was lange bestritten wurde: die tiefe militärische und strategische Verwicklung von Nato-Mitgliedsstaaten in den Ukraine-Krieg. Demnach wird deren Kriegsbeteiligung seit Jahren vom europäischen Hauptquartier der US-Armee in Wiesbaden koordiniert. Für Deutschland stellen sich damit verfassungsrechtliche Fragen.
Und ein Karsten Montag schrieb ebenda am 25. April 2025:
Mehr als drei Jahre nach Beginn des russisch-ukrainischen Krieges berichten zwei große westliche Tageszeitungen über die tiefgreifende Beteiligung von Nato-Militärs an diesem Konflikt. Den Anfang machte die „New York Times“ (NYT). Unter dem Titel „Die Partnerschaft: Die geheime Geschichte des Krieges in der Ukraine“ erschien Ende März ein umfassender *Artikel, der laut Autor Adam Entous auf 300 Interviews mit Regierungs-, Militär- und Geheim-dienstvertretern in der Ukraine, den Vereinigten Staaten sowie weiteren Nato-Partnern basiert. Es handle sich um die „unerzählte Geschichte“ der „versteckten Rolle“ der USA bei den ukrainischen Militäroperationen. *
Wenige Wochen später veröffentlichte die britische Tageszeitung „The Times“ Anfang April einen ähnlichen Beitrag mit dem Titel „Die unerzählte Geschichte der entscheidenden Rolle der britischen Militärchefs in der Ukraine“. Dieser bestätigt die tiefe Verstrickung der Nato-Staaten in Militäroperationen wie der ukrainischen Offensive 2023. Abweichend vom NYT-Artikel bezeichnet er jedoch die britischen Militärchefs als die „Köpfe“ der „Anti-Putin“-Koalition. Einigkeit herrscht wiederum bei der Frage, wer für den Misserfolg der Operationen verantwortlich ist: Dies sei eindeutig der Ukraine zuzuschreiben. Auch im Times-Beitrag wird auf die besondere Rolle des europäischen US-Hauptquartiers im hessischen Wiesbaden bei der Koordination der Einsätze und den Waffenlieferungen hingewiesen.
Na also! Es gibt unter den aus der Ukraine Geflüchteten hier allerdings eine große Mehrheit, die von diesen Fakten weder etwas wissen, noch wissen wollen. Amerika und die Heimat der Anglitschanka ist für sie das Gelobte Land und wehe, du sprichst darüber, dann wirst du sofort der russischen Propaganda verdächtig. Wie Nicki mittlerweile daheim den Knüppel schwingt, interessiert sie auch nicht.
Wieso wird hier nicht untersucht, wieso wird verschwiegen, dass Alexej Nawalny für einen englischen Dienst arbeitete – woher erhielt er das viele Geld für seine Kampagnen? Wo leben nun seine Witwe und die Kinder? Auf der Insel im nebligen Avalon/ Albion…
Ein letztes Beispiel aus dem Bereich der Kultur zum Verständnis des leider so aktuellen Ausdrucks Die Engländerin macht Shit: Anfang 2024 wurde im staatlichen Sender ONE (ARD) eine Serie der BBC zu frühen Erzählungen von Michail Bulgakow ausgestrahlt:** Aufzeichnungen eines jungen Arztes. Die BBC verhunzte den in Kiew geborenen Arzt und weltberühmten Autor derart, dass dem Zuschauer schlecht wurde: Mit dem Titel A Young Doctor‘s Notebook verfilmte sie Bulgakows frühe Erzählungen über die Nöte eines jungen Arztes in der bettelarmen sowjetrussischen Provinz in den 1920er Jahren hypernaturalistisch, blut-, dreck- und eitertriefend. Pseudokyrillische Titel und Balalaika Geklimper begleiteten das Leiden von schwer traumatisierten Menschen im russischen Bürgerkrieg oder Abscheulichkeiten, wie das Amputieren eines Mädchenbeines mit einer Baumsäge - ausgestrahlt vom 1. Deutschen Fernsehen! Michail Bulgakow hätte sich im Grabe umgedreht.
Als Autor beherrschte Bulgakow die Kunst der Groteske ebenso wie hochlyrische Schilderungen. Seine Prosa und seine Theaterstücke aber wurden Zeit seines Lebens von der Sowjetmacht verstümmelt - und post mortem auch von seinen ukrainischen Landsleuten: sein schönes Museum, das ehemalige Domizil der Familie Bulgakow in Kiew am Andrejew-Steig, das mit seinem ersten Roman Die weiße Garde (Kiew vor 100 Jahren im Strudel auch ultranationalistischer Strömungen) und der berühmten Dramatisierung Die Tage der Turbins in die große Literatur einzog, dieses Museum wurde abgewickelt und geschlossen, weil Bulgakow angeblich schlecht über die Ukraine geschrieben hätte!
Ein Glück jedoch, dass die bedeutenden Werke Bulgakows seit nun drei Dekaden von russischsprachigen Philologen beharrlich in ihrer ursprünglichen Fassung wieder hergestellt wurden. Seine großen Romane Die weiße Garde und Meister und Margarita seien in der hervorragenden deutschen Übersetzung von Alexander Nitzberg jedem Interessierten ans Herz gelegt!
Die obigen Ausführungen sind keinesfalls eine Rechtfertigung des Krieges, es geht vielmehr um Hintergründe, Fakten und Machenschaften, die in der Regel bis heute bei uns verschwiegen werden! Obwohl es nun sonnenklar und öffentlich ist, dass bestimmte Inter-essengruppen der englischsprachigen Westmächte die hochgefährliche Konfrontationspolitik mit Russland zu verantworten haben: die Engländerin macht Shit…Und wir? Wir schweigen, glauben der immer noch laufenden Propaganda und wehren uns nicht gegen diese üble Russenphobie?! Ich erinnere mich noch lebhaft an die Nachkriegszeit im Ruhrgebiet, als der Ton ruppig war und Dreck und Trümmer unsere Sicht beherrschten. Auch uns kleinen Kindern gegenüber wurde von den bösen Russen gesprochen, als hätten diese unser Land überfallen.
Ja – es waren viele Geflüchtete aus dem Osten hier gestrandet, und diese hatten Unsägliches hinter sich. Lew Kopelew, der den Einmarsch der Roten Armee in Ostpreußen miterlebte und Gräuel vergebens zu verhindern suchte, wurde noch im April 1945 verhaftet und wegen Mitleid mit dem Feind zu 10 Jahren Lager verurteilt. Viele Jahre später erschienen seine Erinnerungen Aufbewahren für alle Zeit – auch auf Deutsch. Über die mindestens 27 Mio Opfer in der damaligen Sowjetunion und über die deutschen Aggressoren, die damals mit Mord und Raub die bösen Russen, sowjetische Zivilisten überfielen, wurde in den 1950er Jahren, im zerbombten und dreckigen Pott kein einziges Wort verloren. Der Spieß wurde einfach umgedreht. Von der Blockade Leningrads erfuhr ich erst als Erwachsene, anno 1974, als Austauschstudentin vor Ort.
Exakt vor 10 Jahren wurde es jedoch möglich – herzlichen Dank der damaligen stell-vertretenden tatarischen Kulturministerin Frau Irada Ayupova! – mein dokumentarisches Antikriegsstück mit Schicksalen von Kriegskindern – sowjetischen, jüdischen, deutschen – in Kasan, der Hauptstadt von Tatarstan, zweisprachig auf die Bühne des dortigen Jugendtheaters zu bringen. Wir spielten 15 Vorstellungen und einige tausend Jugendliche im Saal verstummten und verstanden, dass Krieg furchtbar ist. Hier und heute will leider kein Theater das Stück umsetzen…
Wir Menschen brauchen Frieden und keine Aufrüstung für neue Kriege! Der gute alte Aischylos schrieb einst in seinem Stück Die Perser: Wahrheit ist das erste Opfer eines Krieges. Leider ist dies immer noch genauso aktuell wie damals. Pfui Teufel!
Jana Moava (Pseudonym) ist Journalistin, Dozentin und arbeitete für große Zeitungen als Korrespondentin.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 3283ef81:0a531a33
2025-05-24 18:20:45
@ 3283ef81:0a531a33
2025-05-24 18:20:45Aliquam eu turpis sed enim ultricies scelerisque\ Duis posuere congue faucibus
Praesent pretium orci ante, et faucibus lectus euismod a
-
 @ c3b2802b:4850599c
2025-05-21 08:47:31
@ c3b2802b:4850599c
2025-05-21 08:47:31In einem Beitrag im Januar 2025 hatte ich das hier kurz schriftlich skizziert. Im April 2025 gab es die Gelegenheit, diese Zusammenhänge etwas ausführlicher im Café mit Katrin Huß darzustellen. Danke, liebe Katrin, für dieses Zusammenkommen in unserer Heimat Sachsen.
Wenn Sie sich für positive Psychologie und deren Einsatz beim Aufbau unserer Regionalgesellschaft interessieren, schauen Sie gern in das 45 -Minuten Gespräch!
Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
-
 @ 21335073:a244b1ad
2025-03-18 20:47:50
@ 21335073:a244b1ad
2025-03-18 20:47:50Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ d61f3bc5:0da6ef4a
2025-05-06 01:37:28
@ d61f3bc5:0da6ef4a
2025-05-06 01:37:28I remember the first gathering of Nostr devs two years ago in Costa Rica. We were all psyched because Nostr appeared to solve the problem of self-sovereign online identity and decentralized publishing. The protocol seemed well-suited for textual content, but it wasn't really designed to handle binary files, like images or video.
The Problem
When I publish a note that contains an image link, the note itself is resilient thanks to Nostr, but if the hosting service disappears or takes my image down, my note will be broken forever. We need a way to publish binary data without relying on a single hosting provider.
We were discussing how there really was no reliable solution to this problem even outside of Nostr. Peer-to-peer attempts like IPFS simply didn't work; they were hopelessly slow and unreliable in practice. Torrents worked for popular files like movies, but couldn't be relied on for general file hosting.
Awesome Blossom
A year later, I attended the Sovereign Engineering demo day in Madeira, organized by Pablo and Gigi. Many projects were presented over a three hour demo session that day, but one really stood out for me.
Introduced by hzrd149 and Stu Bowman, Blossom blew my mind because it showed how we can solve complex problems easily by simply relying on the fact that Nostr exists. Having an open user directory, with the corresponding social graph and web of trust is an incredible building block.
Since we can easily look up any user on Nostr and read their profile metadata, we can just get them to simply tell us where their files are stored. This, combined with hash-based addressing (borrowed from IPFS), is all we need to solve our problem.
How Blossom Works
The Blossom protocol (Blobs Stored Simply on Mediaservers) is formally defined in a series of BUDs (Blossom Upgrade Documents). Yes, Blossom is the most well-branded protocol in the history of protocols. Feel free to refer to the spec for details, but I will provide a high level explanation here.
The main idea behind Blossom can be summarized in three points:
- Users specify which media server(s) they use via their public Blossom settings published on Nostr;
- All files are uniquely addressable via hashes;
- If an app fails to load a file from the original URL, it simply goes to get it from the server(s) specified in the user's Blossom settings.
Just like Nostr itself, the Blossom protocol is dead-simple and it works!
Let's use this image as an example:
 If you look at the URL for this image, you will notice that it looks like this:
If you look at the URL for this image, you will notice that it looks like this:blossom.primal.net/c1aa63f983a44185d039092912bfb7f33adcf63ed3cae371ebe6905da5f688d0.jpgAll Blossom URLs follow this format:
[server]/[file-hash].[extension]The file hash is important because it uniquely identifies the file in question. Apps can use it to verify that the file they received is exactly the file they requested. It also gives us the ability to reliably get the same file from a different server.
Nostr users declare which media server(s) they use by publishing their Blossom settings. If I store my files on Server A, and they get removed, I can simply upload them to Server B, update my public Blossom settings, and all Blossom-capable apps will be able to find them at the new location. All my existing notes will continue to display media content without any issues.
Blossom Mirroring
Let's face it, re-uploading files to another server after they got removed from the original server is not the best user experience. Most people wouldn't have the backups of all the files, and/or the desire to do this work.
This is where Blossom's mirroring feature comes handy. In addition to the primary media server, a Blossom user can set one one or more mirror servers. Under this setup, every time a file is uploaded to the primary server the Nostr app issues a mirror request to the primary server, directing it to copy the file to all the specified mirrors. This way there is always a copy of all content on multiple servers and in case the primary becomes unavailable, Blossom-capable apps will automatically start loading from the mirror.
Mirrors are really easy to setup (you can do it in two clicks in Primal) and this arrangement ensures robust media handling without any central points of failure. Note that you can use professional media hosting services side by side with self-hosted backup servers that anyone can run at home.
Using Blossom Within Primal
Blossom is natively integrated into the entire Primal stack and enabled by default. If you are using Primal 2.2 or later, you don't need to do anything to enable Blossom, all your media uploads are blossoming already.
To enhance user privacy, all Primal apps use the "/media" endpoint per BUD-05, which strips all metadata from uploaded files before they are saved and optionally mirrored to other Blossom servers, per user settings. You can use any Blossom server as your primary media server in Primal, as well as setup any number of mirrors:
 ## Conclusion
## ConclusionFor such a simple protocol, Blossom gives us three major benefits:
- Verifiable authenticity. All Nostr notes are always signed by the note author. With Blossom, the signed note includes a unique hash for each referenced media file, making it impossible to falsify.
- File hosting redundancy. Having multiple live copies of referenced media files (via Blossom mirroring) greatly increases the resiliency of media content published on Nostr.
- Censorship resistance. Blossom enables us to seamlessly switch media hosting providers in case of censorship.
Thanks for reading; and enjoy! 🌸
-
 @ 3283ef81:0a531a33
2025-05-24 18:17:22
@ 3283ef81:0a531a33
2025-05-24 18:17:22Vestibulum a nunc a sapien aliquam rhoncus\ Sed sem turpis, scelerisque sed augue ut, faucibus blandit lectus
Maecenas commodo, augue in placerat lacinia, lorem libero convallis mi, eu fringilla velit arcu id sem. In ac metus vitae sapien dignissim luctus
-
 @ 3c7dc2c5:805642a8
2025-05-24 22:05:00
@ 3c7dc2c5:805642a8
2025-05-24 22:05:00🧠Quote(s) of the week:
'The Cantillon Effect: When new money is printed, those closest to the source (banks, elites) benefit first, buying assets before prices rise. Others lose purchasing power as inflation hits later. If people find out how this works, they will riot.' -Bitcoin for Freedom
Just think about it. Your employer gives you a 5% raise. The Fed (central banks in general) prints 7% more dollars/euros/Fiat. You just got a 2% pay cut. This isn't a conspiracy theory. This is how fiat money steals from the working class every single day. This is why I support Bitcoin.
Anilsaidso: 'Saving in fiat currency is no longer an option. A 2% inflation rate means you lose 1/3 of your purchasing power over 20yrs. At 5% inflation, you lose 60%. And at 10% you've burnt 85%. Reduce your uncertainty. Save in Bitcoin.' https://i.ibb.co/N661BdVp/Gr-Rwdg-OXc-AAWPVE.jpg
🧡Bitcoin news🧡
“Education increases conviction.
Conviction increases allocation.
Allocation increases freedom.” —Gigi
https://i.ibb.co/Q3trHk8Y/Gr-Arv-Ioa-AAAF5b0.jpg
On the 12th of May:
➡️Google searches for "Digital Gold" are at all-time highs. Bitcoin Croesus: "This is the second wave of the Digital Revolution - the digitization of value to complement the Internet's digitization of information. It wasn't possible to own a slice of the Internet itself, but it is possible with Bitcoin, the internet of value." "...It feels like you're late to Bitcoin. But this is a bigger game playing out than most realize, and we are much earlier than casual observers know. If you're reading this, you're here on the frontier early. And you have a chance to stake a claim before 99% of the world shows up. This is a land grab. This is the digital gold rush. Make your descendants proud."
https://i.ibb.co/5XXbNQ8S/Gqw-X4-QRWs-AEd5-Uh-1.jpg
➡️ 'A new holding company ‘Nakamoto’ just raised $710 million to buy more Bitcoin and will merge with KindlyMD to establish a Bitcoin Treasury company. Saylor playbook!' - Bitcoin Archive
➡️American Bitcoin, backed by Donald Trump Jr. and Eric Trump, will go public via an all-stock merger with Gryphon Digital Mining. Post-merger, Trump affiliates and Hut 8 will retain 98% ownership. GRYP tripled to $2.19, Hut 8 jumped 11% to $15.45. The deal closes in Q3 2025.
➡️Phoenix Wallet: 'Phoenix 0.6.0 is out: offers can now have a custom description simple close (set an exact mutual close tx fee rate) native support for Linux arm64 This is the server version. Phoenix mobile release is around the corner. '
On the 13th of May:
➡️Corporate Bitcoin purchases have now outweighed the supply of new Bitcoin by 3.3x in 2025. https://i.ibb.co/fVdgQhyY/Gq1ck-XRXUAAsg-Ym.jpg
➡️ Publicly listed Next Technology disclosed buying 5,000 Bitcoin for $180m, now HODLs 5,833 $BTC worth +$600m.
➡️ After rejecting the Arizona Strategic Bitcoin Reserve Act, Governor Katie Hobbs vetoed Bill SB 1373, which proposed a digital asset reserve fund. "Current volatility in the cryptocurrency markets does not make a prudent fit for general fund dollars."
➡️Meanwhile in Paris, France the kidnapping of a woman with her 2-year-old child morning on the streets of Paris - the target is allegedly the daughter of a crypto CEO. 3 masked men tried forcing them into a fake delivery van, before being fought off by her partner and bystanders. One of whom grabbed a dropped gun and aimed it back.
➡️ 'Bitcoin illiquid supply hit a new all-time high of $1.4B Are you HODLing too, anon?' - Bitcoin News
➡️Why Coinbase entering the S&P 500 matters. Boomers will have Bitcoin / CrApTo exposure, whether they like it or not. Anyway, remember what happened in 2021. The COIN IPO, and they’re still trading about 35% below their IPO-day high. Oh and please read the 'Coinbase" hack below haha.
➡️ Nasdaq listed GD Culture Group to sell up to $300 million shares to buy Bitcoin.
➡️ A Bitcoin wallet untouched since April 2014 just moved 300 BTC worth $31M for the first time in 11 years. This is how you HODL.
➡️ Bitcoin's realized price is steadily increasing, mirroring behaviors seen in past bull markets, according to CryptoQuant.
➡️ Bitcoin whales and sharks (10-10K BTC) accumulated 83,105 BTC in the last 30 days, while small retail holders (<0.1 BTC) sold 387 BTC, according to Santiment.
Bitcoin Whales have been AGGRESSIVELY accumulating BTC recently! With at least 240,000+ Bitcoin transferred to wallets with at least 100 BTC. The largest market participants are trying to buy as much as possible, what do they think comes next...
➡️'The average cost of mining 1 BTC for miners is currently $36.8K. The spread between the current market price and the cost of one coin = 182%. This is essentially the average profitability. This corresponds to the beginning of the bull cycle in November 2022 and the peaks of this cycle >$100K. A price increase above this level will allow miners to fully recover after the last halving and reach excess profits comparable to the beginning of the bull rally in January 2023.' -Axel Adler Jr.
➡️ Remember last week's segment on Coinbase..."Coinbase just disclosed in their Q1 filing: that they have custody of 2.68 million Bitcoin. That’s over 13% of all Bitcoin in circulation, on one platform. Is this the greatest honeypot in financial history? Yes, it is...read next week's Weekly Bitcoin update."
Well, here you go.
Coinbase estimates $180-$400 million in losses, remediation costs, and reimbursement following today’s cyber attack. https://i.ibb.co/jkysLtZ1/Gq-C7zl-W4-AAJ0-N6.jpg
Coinbase didn't get hacked. Coinbase employees sold customer data on the black market. Coinbase failed to protect customer data. This is why KYC is useless. The criminals have our driver's license scans. They have AI tools that can generate fake images and videos. KYC puts our identities at risk, makes onboarding more difficult, and rewards criminals. To make it even worse. Coinbase knew about the hack as early as January but only disclosed it publicly after being added to the S&P 500.
I will say it one more time! Don't buy your Bitcoin on KYC exchanges. KYC means handing over your identity to be leaked, sold, or extorted.
It was 2 days ago, see the bit on the 13th of May, that we saw a violent attack in Paris. Minimize the data you share with centralized tools. Store as much as you can locally. Always ask yourself what data am I giving and to whom? Remove the need for trust.
And for the love of God, Allah, or whatever god you are praying to...
DON'T LEAVE YOUR COINS ON A FREAKING EXCHANGE!!!!
Clear!
➡️ Sam Callahan: Bitcoin CAGRs over rolling four-year holding periods since 2012:
10th percentile: 33%
25th percentile: 50% 40th percentile: 75%
Said differently, for 90% of the time, Bitcoin’s four-year CAGR was higher than 33%. For comparison, here are the single best four-year CAGRs over the same period for:
Gold: 17%
Silver: 20%
S&P 500: 24%
Apple: 52%
Two lessons here:
1.) Even when Bitcoin underperforms, it still outperforms.
2.) Bitcoin holding goals are best measured in halving cycles.'
https://i.ibb.co/9m6q2118/Gq1-Ie2-Ob-AAIJ8-Kf.jpg
➡️ Deutsche Bank Aktiengesellschaft has bought 96,870 Strategy₿ stocks for 30 Million dollars at an Average Price Of $310 Per Share In Q1 2025, Their Total Holdings Is 518,000 Shares Worth Over 214 Million Dollars.
➡️Senator Lummis urges the U.S. Treasury to eliminate taxes on unrealized gains for Bitcoin.
On the 14th of May:
➡️At $168,000, Bitcoin will surpass Microsoft, the world's largest company.
➡️Fidelity tells institutions to buy Bitcoin if they can’t match Bitcoin’s 65% return on capital.
➡️Michigan has adopted House Resolution 100, declaring May 13 2025 as "Digital Asset Awareness Day." The resolution encourages "activities and programs that foster a deeper understanding of digital assets and their impact on our society and economy."
➡️Publicly traded Vinanz raises funding to buy $2 million in #Bitcoin assets.
➡️Bitcoin News: "Investor Jim Chanos is shorting MicroStrategy while going long on Bitcoin, calling the stock overvalued relative to its BTC holdings. “We’re selling MicroStrategy and buying Bitcoin, basically buying something for $1 and selling it for $2.50," he told CNBC
On the 15th of May:
➡️The Abu Dhabi sovereign wealth fund disclosed owning $511 million in Bitcoin through BlackRock’s ETF.
➡️UK public company Coinsilium Group raises £1.25 million to adopt a Bitcoin treasury strategy.
➡️Chinese Textile company Addentax issues stock to buy 8,000 Bitcoin.
➡️14 US states have reported $632m in $MSTR exposure for Q1, in public retirement and treasury funds. A collective increase of $302m in one quarter. The average increase in holding size was 44%.
➡️Chinese public company DDC Enterprise to adopt a Bitcoin Reserve with 5,000 BTC.
On the 16th of May:
➡️Brazilian listed company Méliuz buys $28.4 million Bitcoin to become the nation's first Bitcoin Treasury Company. Shareholders voted to approve the strategy by an "overwhelming majority".
➡️13F Filings show Texas Retirement System owns MSTR. The day MSTR enters the S&P 500, every pension fund will follow.
➡️'Wealthy Investors Shift Up to 5% into Bitcoin as confidence in fiat falters. UBS, a Swiss banking giant says Bitcoin and digital assets are becoming key hedges against inflation and systemic risk, marking a dramatic shift in modern portfolio strategy.' -CarlBMenger
➡️River: "Above all, Bitcoin is money for the people." https://i.ibb.co/Jj8MVQwr/Gr-Ew-EPp-XAAA1-TVN.jpg
On the 17th of May:
➡️Illicit activity is now down to 0.14% of transaction volume across all crypto.
Context: World Bank, IMF suggests 1.5–4% of global GDP is laundered yearly through traditional banking Of that 0.14%:
63% of illicit trade was stablecoins.
13% was Bitcoin (declining each year)
Source: The 2025 Crypto Crime Report, Chainalysis 2025
Yet another confirmation that Bitcoin's use in facilitating illicit activities is a rounding error on a rounding error.
On the 18th of May:
➡️JPMorgan CEO Jamie Dimon said they will allow clients to buy Bitcoin. The repeal of SAB 121 is a bigger deal than most realize. “I will fire any employee buying or trading Bitcoin for being stupid” - Jamie Dimon (2017) https://i.ibb.co/b5tnkb15/Gr-Vxxc-OXk-AA7cyo.jpg
On the 19th of May.
➡️Bookmark the following stuff from Daniel Batten if you want to combat climate change (fanatics)...
'That Bitcoin mining is not only not harmful, but beneficial to the environment is now supported by:
7 independent reports
20 peer-reviewed papers
As a result * 90% of climate-focused magazines * 87.5% of media coverage on Bitcoin & the environment is now positive * source 7 independent reports https://x.com/DSBatten/status/1922666207754281449… * 20 peer-reviewed papers https://x.com/DSBatten/status/1923014527651615182… * 10 climate-focused magazines https://x.com/DSBatten/status/1919518338092323260… * 16 mainstream media articles https://x.com/DSBatten/status/1922628399551434755
➡️Saifedean Ammous: '5 years ago at the height of corona hysteria, everyone worried about their savings.
If you put $10,000 in "risk-free" long-term US government bonds, you'd have $6,000 today.
If you put the $10,000 in "risky speculative tulip" bitcoin, you'd have $106,000.
HFSP, bondcucks!'
I love how Saifedean always put it so eloquently. haha
➡️An Australian judge rules Bitcoin is “just another form of money.” This could make it exempt from capital gains tax. Potentially opening the door to millions in refunds across the country. - AFR
If upheld, the decision could trigger up to $1B in refunds and overturn the Australian Tax Office’s crypto tax approach.
➡️Publicly traded Vinanz buys 16.9 Bitcoin for $1.75 Million for their treasury.
➡️Bitcoin just recorded its highest weekly close ever, while the Global Economic Policy Uncertainty Index hit its highest level in history.
➡️4 in 5 Americans want the U.S. to convert part of its gold reserves to Bitcoin. - The Nakamoto Project
"or background, the survey question was: "Assuming the United States was thinking of converting some of their gold reserves into Bitcoin, what percentage would you advise they convert?" Respondents were provided a slider used to choose between 0% and 100%. Our survey consisted of a national sample of 3,345 respondents recruited in partnership with Qualtrics, a survey and data collection company"
Context: https://x.com/thetrocro/status/1924552097565180107 https://i.ibb.co/fGDw06MC/Gr-VYDIdb-AAI7-Kxd.jpg
➡️Michael Saylor's STRATEGY bought another $764.9m Bitcoin. They now HODL 576,230 Bitcoin, acquired for $40.18 billion at $69,726 per Bitcoin.
➡️The German Government sold 49,858 BTC for $2.89B, at an average price of $57,900. If they had held it, their BTC would now be worth $5.24B.
➡️A record 63% of all the Bitcoin that exist have not transacted or moved from their wallets this year. - Wicked
https://i.ibb.co/j9nvbvmP/Gq3-Z-x6-Xw-AAv-Bhg.jpg
💸Traditional Finance / Macro:
On the 12th of May:
👉🏽The S&P 500 has closed more than 20% above its April low, technically beginning a new bull market. We are now up +1,000 points in one month.
On the 13th of May:
👉🏽 Nvidia announces a partnership with Humain to build "AI factories of the future" in Saudi Arabia. Just one hour ago, Saudi Arabia signed an economic agreement with President Trump to invest $600 billion in the US.
🏦Banks:
👉🏽 No news
🌎Macro/Geopolitics:
On the 12th of May:
👉🏽Huge pressure is on the European Union to reach a trade deal. Equities and commodities bounce hard on news of China-US trade deal. "We have reached an agreement on a 90-day pause and substantially moved down the tariff levels — both sides, on the reciprocal tariffs, will move their tariffs down 115%." - Treasury Secretary Scott Bessent
Dollar and Yuan strong bounce. Gold corrects.
👉🏽After reaching a high of 71% this year, recession odds are now back down to 40%. The odds of the US entering a recession in 2025 fall to a new low of 40% following the US-China trade deal announcement.
👉🏽'Truly incredible:
- Trump raises tariffs: Yields rise because inflation is back
- Trump cuts tariffs: Yields rise because growth is back
- Trump does nothing: Yields rise because the Fed won't cut rates Today, the bond market becomes Trump and Bessent's top priority.' - TKL
President Trump’s biggest problem persists even as trade deals are announced. Tariffs have been paused for 90 days, the US-China trade deal has been announced, and inflation data is down. Yet, the 10Y yield is nearing 4.50% again. Trump needs lower rates, but rates won’t fall.
👉🏽Last week a lot of talk on Japan’s Debt Death Spiral: Japan’s 40-year yield is detonating and the myth of consequence-free debt just died with it. One of the best explanations, you can read here:
👉🏽Michael A. Arouet: 'Eye-opening chart. Can a country with a services-based economy remain a superpower? Building back US manufacturing base makes a lot of strategic and geopolitical sense.' https://i.ibb.co/Q3zJY9Fc/Gqxc6-Pt-WQAI73c.jpg
On the 13th of May:
👉🏽There is a possibility of a “big, beautiful” economic rebalancing, Treasury Secretary Scott Bessent says at an investment forum in Saudi Arabia. The “dream scenario” would be if China and the US can work together on rebalancing, he adds
Luke Gromen: It does roll off the tongue a whole lot nicer than "We want to significantly devalue USD v. CNY, via a gold reference point."
Ergo: The price of gold specifically would rise in USD much more than it would in CNY, while prices for other goods and services would not, or would do so to a lesser degree.
👉🏽 Dutch inflation rises to 4.1 percent in April | CBS – final figure. Unchanged compared to the estimate.
👉🏽Philipp Heimberger: This interesting new paper argues that cuts to taxes on top incomes disproportionately benefit the financial sector. The finance industry gains more from top-income tax cuts than other industries. "Cuts in top income tax rates increase the (relative) size of the financial sector"
Kinda obvious, innit?
👉🏽US CPI data released. Overall good results and cooler than expected month-over-month and year-over-year (outside of yearly core). U.S. inflation is down to 2.3%, lower than expected.
On the 14th of May:
👉🏽'The US government cannot afford a recession: In previous economic cycles, the US budget deficit widened by ~4% of GDP on average during recessions. This would imply a ~$1.3 trillion deterioration of US government finances if a recession hits in 2025. That said, if the US enters a recession, long-term interest rates will likely go down.
A 2-percentage-point decrease in interest rates would save ~$568 billion in annual interest payments. However, this means government finances would worsen by more than DOUBLE the amount saved in interest due to a recession. An economic downturn would be incredibly costly for the US government.' -TKL
On the 15th of May:
👉🏽'In the Eurozone and the UK, households hold more than 30% of their financial assets in fiat currencies and bank deposits. This means that they (unknowingly?) allow inflation to destroy their purchasing power. The risks of inflation eating up your wealth increase in a debt-driven economic system characterized by fiscal dominance, where interest rates are structurally low and inflation levels and risks are high. There is so much forced and often failed regulation to increase financial literacy, but this part is never explained. Why is that, you think?' - Jeroen Blokland https://i.ibb.co/zWRpNqhz/Gq-jn-Bn-X0-AAmplm.png
On the 16th of May:
👉🏽'For the first time in a year, Japan's economy shrank by -0.7% in Q1 2025. This is more than double the decline expected by economists. Furthermore, this data does NOT include the reciprocal tariffs imposed on April 2nd. Japan's economy is heading for a recession.' -TKL
👉🏽'246 US large companies have gone bankrupt year-to-date, the most in 15 years. This is up from 206 recorded last year and more than DOUBLE during the same period in 2022. In April alone, the US saw 59 bankruptcy filings as tariffs ramped up. So far this year, the industrials sector has seen 41 bankruptcies, followed by 31 in consumer discretionary, and 17 in healthcare. According to S&P Global, consumer discretionary companies have been hit the hardest due to market volatility, tariffs, and inflation uncertainty. We expect a surge in bankruptcies in 2025.' -TKL
👉🏽'Moody's just downgraded the United States' credit rating for the FIRST time in history. The reason: An unsustainable path for US federal debt and its resulting interest burden. Moody's notes that the US debt-to-GDP ratio is on track to hit 134% by 2035. Federal interest payments are set to equal ~30% of revenue by 2035, up from ~18% in 2024 and ~9% in 2021. Furthermore, deficit spending is now at World War 2 levels as a percentage of GDP. The US debt crisis is our biggest issue with the least attention.' - TKL
Still, this is a nothing burger. In August 2023, when Fitch downgraded the US to AA+, and S&P (2011) the US became a split-rated AA+ country. This downgrade had almost no effect on the bond market. The last of the rating agencies, Moodys, pushed the US down to AA+ today. So technically it didn’t even change the US’s overall credit rating because it was already split-rated AA+, now it’s unanimous AA+.
Ergo: Nothing changed. America now shares a credit rating with Austria and Finland. Hard assets don’t lie. Watch Gold and Bitcoin.
https://i.ibb.co/Q7DcWY2P/Gr-K66i-EXIAAKh-MR.jpg
RAY DALIO: Credit Agencies are UNDERSTATING sovereign credit risks because "they don't include the greater risk that the countries in debt will print money to pay their debts" with devalued currency.
👉🏽US consumer credit card serious delinquencies are rising at a CRISIS pace: The share of US credit card debt that is past due at least 90 days hit 12.3% in Q1 2025, the highest in 14 YEARS. The percentage has risen even faster than during the Great Financial Crisis.' - Global Markets Investor
https://i.ibb.co/nNH9CxVK/Gr-E838o-XYAIk-Fyn.png
On the 18th of May:
👉🏽Michael A. Arouet: 'Look at ten bottom of this list. Milei has not only proven that real free market reforms work, but he has also proven that they work fast. It’s bigger than Argentina now, no wonder that the left legacy media doesn’t like him so much.' https://i.ibb.co/MDnBCDSY/Gr-Npu-KKWMAAf-Pc.jpg
On the 19th of May: 👉🏽Japan's 40-year bond yield just hit its highest level in over 20 years. Japan’s Prime Minister Ishiba has called the situation “worse than Greece.” All as Japan’s GDP is contracting again. You and your mother should be scared out of your fucking minds. https://i.ibb.co/rGZ9cMtv/GTXx-S7-Cb-MAAOu-Vt.png
👉🏽 TKL: 'Investors are piling into gold funds like never before: Gold funds have posted a record $85 BILLION in net inflows year-to-date. This is more than DOUBLE the full-year record seen in 2020. At this pace, net inflows will surpass $180 billion by the end of 2025. Gold is now the best-performing major asset class, up 22% year-to-date. Since the low in October 2022, gold prices have gained 97%. Gold is the global hedge against uncertainty.'
🎁If you have made it this far, I would like to give you a little gift, well, in this case, two gifts:
What Bitcoin Did - IS THE FED LOSING CONTROL? With Matthew Mezinskis
'Matthew Mezinskis is a macroeconomic researcher, host of the Crypto Voices podcast, and creator of Porkopolis Economics. In this episode, we discuss fractional reserve banking, why it's controversial among Bitcoiners, the historical precedent for banking practices, and whether fractional reserve banking inherently poses systemic risks. We also get into the dangers and instabilities introduced by central banking, why Bitcoin uniquely offers a pathway to financial sovereignty, the plumbing of the global financial system, breaking down money supply metrics, foreign holdings of US treasuries, and how all these elements indicate growing instability in the dollar system.'
https://youtu.be/j-XPVOl9zGc
Credit: I have used multiple sources!
My savings account: Bitcoin The tool I recommend for setting up a Bitcoin savings plan: PocketBitcoin especially suited for beginners or people who want to invest in Bitcoin with an automated investment plan once a week or monthly.
Use the code SE3997
Get your Bitcoin out of exchanges. Save them on a hardware wallet, run your own node...be your own bank. Not your keys, not your coins. It's that simple. ⠀ ⠀
⠀⠀ ⠀ ⠀⠀⠀
Do you think this post is helpful to you?
If so, please share it and support my work with a zap.
▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃
⭐ Many thanks⭐
Felipe - Bitcoin Friday!
▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃
-
 @ 866e0139:6a9334e5
2025-05-19 21:39:26
@ 866e0139:6a9334e5
2025-05-19 21:39:26Autor: Ludwig F. Badenhagen. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie auch in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Wer einhundert Prozent seines Einkommens abgeben muss, ist sicher ein Sklave, oder? Aber ab wieviel Prozent Pflichtabgabe ist er denn kein Sklave mehr? Ab wann ist er frei und selbst-bestimmt?
Wer definieren möchte, was ein Sklave ist, sollte nicht bei Pflichtabgaben verweilen, denn die Fremdbestimmtheit geht viel weiter. Vielfach hat der gewöhnliche Mensch wenig Einfluss darauf, wie er und seine Familie misshandelt wird. Es wird verfügt, welche Bildung, welche Nahrung, welche Medikamente, welche Impfungen und welche Kriege er zu erdulden hat. Hierbei erkennt der gewöhnliche Mensch aber nur, wer ihm direkt etwas an-tut. So wie der Gefolterte bestenfalls seinen Folterer wahrnimmt, aber nicht den, in dessen Auftrag dieser handelt, so haben die vorbezeichnet Geschädigten mit Lehrern, „Experten“, Ärzten und Politikern zu tun. Ebenfalls ohne zu wissen, in wessen Auftrag diese Leute handeln. „Führungssysteme“ sind so konzipiert, dass für viele Menschen bereits kleinste wahrgenommene Vorteile genügen, um einem anderen Menschen Schlimmes anzutun.
Aber warum genau wird Menschen Schlimmes angetan? Die Gründe dafür sind stets dieselben. Der Täter hat ein Motiv und Motivlagen können vielfältig sein.
Wer also ein Motiv hat, ein Geschehen zu beeinflussen, motiviert andere zur Unterstützung. Wem es gelingt, bei anderen den Wunsch zu erwecken, das zu tun, was er möchte, ist wirklich mächtig. Und es sind die Mächtigen im Hintergrund, welche die Darsteller auf den Bühnen dieser Welt dazu nutzen, die Interessen der wirklich Mächtigen durchzusetzen. Insbesondere die letzten fünf Jahre haben eindrucksvoll gezeigt, wie willfährig Politiker, Ärzte, Experten und viele weitere ihre jeweiligen Aufträge gegen die Bevölkerung durchsetz(t)en.
Und so geschieht es auch beim aktuellen Krieg, der stellvertretend auf dem europäischen Kontinent ausgetragen wird. Parolen wie „nie wieder Krieg“ gehören der Vergangenheit an. Stattdessen ist nunmehr wieder der Krieg und nur der Krieg geeignet, um „Aggressionen des Gegners abzuwehren“ und um „uns zu verteidigen“.
Das hat mindestens drei gute Gründe:
- Mit einem Krieg können Sie einem anderen etwas wegnehmen, was er freiwillig nicht herausrückt. Auf diese Weise kommen Sie an dessen Land, seine Rohstoffe und sein Vermögen. Sie können ihn beherrschen und Ihren eigenen Einfluss ausbauen. Je mehr Ihnen gehört, um so besser ist das für Sie. Sie müssen sich weniger abstimmen und Widersacher werden einfach ausgeschaltet.
- Wenn etwas über einen langen Zeitraum aufgebaut wurde, ist es irgendwann auch einmal fertig. Um aber viel Geld verdienen und etwas nach eigenen Vorstellungen gestalten zu können, muss immer wieder etwas Neues erschaffen werden, und da stört das Alte nur. Demzufolge ist ein Krieg ein geeignetes Mittel, etwas zu zerstören. Und das Schöne ist, dass man von Beginn an viel Geld verdient. Denn man muss dem indoktrinierten Volk nur vormachen, dass der Krieg „unbedingt erforderlich“ sei, um das Volk dann selbst bereitwillig für diesen Krieg bezahlen und auch sonst engagiert mitwirken zu lassen. Dann kann in Rüstung und „Kriegstauglichkeit“ investiert werden. Deutschland soll dem Vernehmen nach bereits in einigen Jahren „kriegstauglich“ sein. Der Gegner wartet sicher gerne mit seinen Angriffen, bis es so weit ist.
- Und nicht zu vergessen ist, dass man die vielen gewöhnlichen Menschen loswird. Schon immer wurden Populationen „reguliert“. Das macht bei Tieren ebenfalls so, indem man sie je nach „Erfordernis“ tötet. Und bei kollabierenden Systemen zu Zeiten von Automatisierung und KI unter Berücksichtigung der Klimarettung wissen doch mittlerweile alle, dass es viel zu viele Menschen auf dem Planeten gibt. Wenn jemand durch medizinische Misshandlungen oder auch durch einen Krieg direkt stirbt, zahlt dies auf die Lösung des Problems ein. Aber auch ein „Sterben auf Raten“ ist von großem Vorteil, denn durch die „fachmännische Behandlung von Verletzten“ bis zu deren jeweiligen Tode lässt sich am Leid viel verdienen.
Sie erkennen, dass es sehr vorteilhaft ist, Kriege zu führen, oder? Und diese exemplarisch genannten drei Gründe könnten noch beliebig erweitert werden.
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes.
Das Einzige, was gegen Kriegsereignisse sprechen könnte, wäre, dass man selbst niemandem etwas wegnehmen möchte, was ihm gehört, und dass man seinen Mitmenschen nicht schaden, geschweige denn diese verletzen oder gar töten möchte.
In diesem Zusammenhang könnte man auch erkennen, dass die, die nach Krieg rufen, selbst nicht kämpfen. Auch deren Kinder nicht. Man könnte erkennen, dass man selbst nur benutzt wird, um die Interessen anderer durchzusetzen. Wie beim Brettspiel Schach hat jede Figur eine Funktion und keinem Spieler ist das Fortbestehen eines Bauern wichtig, wenn seine Entnahme dem Spielgewinn dient. Wer Krieg spielt, denkt sicher ähnlich.
Meine beiden Großväter waren Soldaten im zweiten Weltkrieg und erlebten die Grausamkeiten des Krieges und der Gefangenschaft so intensiv, dass sie mit uns Enkeln zu keiner Zeit hierüber sprechen konnten, da sie wohl wussten, dass uns allein ihre Erzählungen zutiefst traumatisiert hätten. Die Opas waren analog dem, was wir ihnen an Information abringen konnten, angeblich nur Sanitäter. Sanitäter, wie auch die meisten Großväter aus der Nachbarschaft. Wer aber jemals beobachten konnte, wie unbeholfen mein Opa ein Pflaster aufgebracht hat, der konnte sich denken, dass seine vermeintliche Tätigkeit als Sanitäter eine Notlüge war, um uns die Wahrheit nicht vermitteln zu müssen.
Mein Opa war mein bester Freund und mir treibt es unverändert die Tränen in die Augen, sein erlebtes Leid nachzuempfinden. Und trotz aller seelischen und körperlichen Verletzungen hat er nach seiner Rückkehr aus der Kriegshölle mit großem Erfolg daran gearbeitet, für seine Familie zu sorgen.
Manchmal ist es m. E. besser, die Dinge vom vorhersehbaren Ende aus zu betrachten, um zu entscheiden, welche Herausforderungen man annimmt und welche man besser ablehnt. Es brauchte fast 80 Jahre, um die Deutschen erneut dafür zu begeistern, Ihre Leben „für die gute Sache“ zu opfern. Was heutzutage aber anders ist als früher: Einerseits sind die Politiker dieser Tage sehr durchschaubar geworden. Aber in einem ähnlichen Verhältnis, wie die schauspielerischen Leistungen der Politiker abgenommen haben, hat die Volksverblödung zugenommen.
Denken Sie nicht nach. Denken Sie stattdessen vor. Und denken Sie selbst. Für sich, Ihre Lieben und alle anderen Menschen. Andernfalls wird die Geschichte, so wie sie von meinen Opas (und Omas) erlebt wurde, mit neuen Technologien und „zeitgemäßen Methoden“ wiederholt. Dies führt zweifelsfrei zu Not und Tod.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ bf47c19e:c3d2573b
2025-05-24 18:17:09
@ bf47c19e:c3d2573b
2025-05-24 18:17:09Ovaj post sam objavio 24.01.2024. godine na Redditu povodom tri decenije od uvođenja Novog dinara kao rešenja za hiperinflaciju u Saveznoj Republici Jugoslaviji na šta su pojedini besni nokoineri sa te društvene mreže osuli drvlje i kamenje na mene. Od starih budalaština da je Bitkoin bezvredan, da nije oblik novca već finansijsko ulaganje, preko pravdanja svrhe inflacije, sve do potpune nemoći da se argumentima opovrgne nepobitna istina i pozivanja moderatora da me banuju. 🙃
Cena Bitkoina tada je bila oko $40.000. :)
Osim glavnog posta, ovde ću navesti i moje odgovore na neutemeljene i neinformisane tvrdnje besnih nokoinera. :) Da se sačuva od zaborava!
Juče se navršilo 30 godina "Deda Avramove reforme".
Dan kada je rođen novi dinar, a Deda Avram sasekao hiperinflaciju
Dva jajeta – nedeljna profesorska plata: Kako se živelo u hiperinflaciji i šta je uradio Avramović
Vikipedija: Jugoslovenski dinar
„U julu '93. godine u Jugoslaviji nisi mogao skoro ništa da kupiš i niko za dinare nije hteo ništa da prodaje“, pisao je Avramović. Centralno-bankarska prevara se nastavlja jer je već do kraja 1995. dinar oslabio prema marki za 70% (1 dinar = 3.4 DM), a u decembru 2000. je taj kurs već bio 30.5 dinara za 1 DM (-96.7% od uvođenja novog dinara). To samo pokazuje da redenominacija valute tj. "brisanje nula" nije nikako čudo i viđano je puno puta kroz istoriju)
Ako je reformom iz januara '94 god. 1 novi dinar vredeo kao 1 nemačka marka, zatim od 2002. uveden evro čime je realna vrednost marke (samim tim i dinara) prepolovljena, a danas 1 EUR vredi oko 117 RSD, to znači da je "deda Avramov dinar" prema evru već obezvređen 59.91 puta za 30 godina. Dakle devalvacija dinara od 5991% od 1994. godine, a svakako još veća izražena kroz dobra i usluge jer su i nemačka marka do 2002. i evro od svog uvođenja iste godine prošli kroz sopstvenu inflaciju. Sam evro je izgubio oko 38% vrednosti od 2002. godine. Tako da se može reći da i "deda Avramov dinar" već uveliko prolazi kroz hiperinflaciju koja je samo razvučena na mnogo duži vremenski period (ne brinite - znam "zvaničnu" definiciju hiperinflacije - još jedan "gaslighting" centralno-bankarskog kartela da zabašuri šta se iza brda valja). Jer šta je inflacija od preko 5991% nego višedecenijska hiperinflacija?! Kako ne shvata gigantske razmere ove prevare?!
ISPRAVKA: Dinar nije nominalno izgubio 23400% (234x) vrednosti prema nemačkoj marki/evru od 1994. godine, već 59.91x odnosno 5991%. I danas na sajtu NBS postoji zvanični srednji kurs marke prema dinaru od 59,91:1. Realno, obezvređivanje dinara i evra prema robama i uslugama je puno veće, pošto su cene roba i usluga izražene u evrima ubrzo udvostručene u periodu nakon uvođenja evra. Hvala članu DejanJwtq na ispravci i izvinjenje svima od mene zbog greške.
Dafiment i Jugoskandik ("Dafina i Jezda") su bili samo državna konstrukcija da se izvuku devize iz ruku naivnih investitora da bi te devize nešto kasnije poslužile kao tobožnja rezerva za novi dinar. Ova gigantska prevara je unapred bila planirana, a Deda Avram iskorišćen kao marioneta tadašnjeg režima.
Inače lista država koje su izvršile redenominaciju valute kroz "brisanje nula" je poprilično dugačka i radi se o uobičajenoj pojavi kroz istoriju još od Haitija 1813. godine, a poslednji put su to uradile Sijera Leone i Kolumbija 2021. godine. Odavno je zaboravljeno da je (SR) Jugoslavija devedesetih to učinila još 1990. (10.000:1), 1992. (10:1), 1993. (1.000.000:1) i 1994. pre Avramovića (1.000.000.000∶1) ali je ovaj dinar trajao samo 23 dana. Tako da Deda Avram nije izmislio toplu vodu.
U SFRJ je izvršena jedna redenominacija 1966. godine u odnosu 10.000:1.
Wikipedia: Redenomination
Kome i dalje nije jasno zašto Bitkoin neka više puta pažljivo pročita ove tekstove iznad: oblik novca koji se ne može redenominirati, veoma lako konfiskovati i izdavati bez ikakve kontrole i pokrića. Potpuno nezavistan od kaprica korumpiranih i od realnosti otuđenih političara i centralnih bankara. Veoma je bitno da postoji ovakav oblik novca koji nije podložan ovakvim manipulacijama od strane ljudskog faktora i da postoji slobodan izbor da se taj oblik novca odabere za štednju i transakcije: barem od strane onih koji ga razumeju, ovi koji ne žele da razumeju neka i dalje pristaju da budu pljačkani - njima ionako nema pomoći.
Komentari
brainzorz: Da, ali ako cemo realno bitkoin ne sluzi kao oblik novca, vec kao finansijsko ulaganje.
Bar je tako za nas i vecinu ljudi po svetu u praktičnom smislu. Jer 99.99% ljudi ili koliko vec prime platu u svojoj lokalnoj valuti, trose istu na redovan zivot, a ostatak (ako ga ima) investiraju. Slazem se da lokalne valute imaju svoj neki rizik, koji je veci u banana drzavi i da cuvanje svog kapitala u turbulentnom periodu u istoj je jako losa ideja.
Kada tako posmatras onda se mogu vuci pararele izmedju ostalih aseta, poput ETFova na primer i onda dolazimo do gomile problema sa bitkoinom.
@BTCSRB: Bitkoin se ne može porediti sa ETF-ovima pošto ETF-ove i ostale investicione instrumente ne možeš koristiti kao novac jer oni nisu "bearer assets" kao što jeste BTC. BTC eliminiše potpuno inflaciju (jer džabe ti keš u slamarici kao "bearer asset" kada je podložan inflaciji) i potrebu za posrednikom kod elektronskih plaćanja.
brainzorz: Ali on to eleminise samo u teoriji, sad da odem u pekaru, moram platiti u lokalnoj valuti, sad da li cu prodati bitkoin ili etf, prilicno je slicno.
Jedino sto mogu bitkoin zamenuti uzivo (ilegalno) sa nekim, pa tu jeste zamenjen posrednik. Ali provizije povlacenja su uglavnom zanemarljive, naspram ostalih parametara investicionog sredstva.
Neke stvari se mogu direktno platiti za bitkoin, ali to je ekstremno retko u stvarnom zivotu vecine ljudi.
@BTCSRB: Slažem se ali u uslovima hiperinflacije i visoke inflacije kakvu danas imamo u Argentini, Venecueli, Zimbabveu, Libanu, Turskoj itd. sve više ljudi direktno vrši transakcije u kriptovalutama, naročito "stablecoinima" poput USDT Tethera. Priznajem da u tim transakcijama BTC zaostaje upravo zbog volatilnosti ali je vršenje brzih i jeftinih transakcija svakako moguće putem Lightning mreže. Sve te lokalne valute su izgubile značajnu vrednost i prema USDT i prema BTC-u, odnosno BTC konstantno probija rekordnu vrednost kada se denominuje u tim valutama. I u tim državama je adopcija kriptovaluta najraširenija.
HunterVD: Kako valuta u koju se upumpavaju nepostojeci dolari i evri moze biti realna i dobra. A USDT tek da ne spominjem. Mozes uvek revi jer joj ljudi veruju, al ta vera u nesto ide samo do odredjenog nivoa.
@BTCSRB: Godinama kupujem BTC od svake plate, praktično štedim u njemu i kupovna moć mi vremenom raste denominirana u evrima i dinarima. To isto rade na desetine hiljada ljudi širom sveta. Kako su ti realni dinari i evri koje ubacujem svakog meseca koje sam zaradio od svog realnog rada - "nepostojeći"?
Kako dolari i evri koji se štampaju ni iz čega mogu biti realni i dobri kao valuta?
HunterVD: Pa eto bas to. Ulaze se nepostojeci novac u BTC i onda se prica o nekoj novoj valuti. Nije sija nego vrat, BTC ima jedino vrednost dok se upumpava taj lazni novac u njega. FIAT novac kolko tolko nastaje radom i proizvodnjom dobara, ne sav FIAT novac al neki deo, dok se BTC zasniva skroz na upumpavanje tog istog FIAT novca i dobroj volji i zeljama da magicne brojke idu navise.
@BTCSRB: Itekako je moguće izraziti cenu svih ostalih dobara i usluga kroz BTC i postojanje i vrednost BTC-a uopšte ne zavisi od fiat novca. Štaviše, gotova sva dobra i usluge dugoročno postaju jeftiniji kada se mere kroz BTC. Sutra kada bi fiat novac nestao BTC bi i dalje imao vrednost, čak i veću nego danas.
https://www.pricedinbitcoin21.com/
HunterVD: Naravno da je moguce izraziti cene svakodnevnih proizvoda u BTCu. Cene svakodnevnih proizvoda je moguce izraziti u cemu god pozelis, evo npr broj radnih sati koji je potreban da se proizvede taj proizvod i onda se uporedi sa cenom radnih sati i cene na polici, mozes ga uracunavati i u dobrima , jedan iphone kosta tolko i tolko KG juneceg mesa..... nista cudno. Takodje cene proizvoda pokazuju pad u odnosu sa BTCom jer je BTC masivno porastao u poslednjih 5-6 godina. Sta ce biti kad BTC stagnira ili pada kako se u tom periodu odnose cene, a da BTC je store of value i namenjen je samo da se cuva izvinte molim vas moja greska. Ni druge kripto valute nisu nista bolje. Ljudi koji su zaradili na BTCu svaka cast eto imali su pameti i srece , al sad kako je cena sve veca, inflacija sve losija i kamatne stope sve vise postace sve teze i teze dolaziti do novca a kamo li intvestirati ga u nesto rizicno ko kripto valute tako da ce i BTC sve manje rasti sto zbog velicine market cap-a sto zbog toga sto ljudi i firme imaju sve manje novca za ulagati. Dal ce btc moci da se uzbori sa inflacijom i losim uslovima to tek treba da se vidi. Tako da videcemo u narednom periodu koliko ce se ta priva o BTC kao store of value i nacinu odbrane od inflacije obistiniti. Licno ne verujem da ce BTC ikad biti zvanicno sredstvo placanja.
@BTCSRB: Cena svega se može izraziti kroz sve ostalo ali šta od svega toga najbolje vrši funkciju novca? BTC bolje vrši funkciju novca u većini okolnosti od gotovo svih stvari.
Šta će biti sa BTC videće se i oni koji veruju u njega će biti najzaslužniji za njegov uspeh jer su obezbeđivali potražnju kada su kola išla nizbrdo i za to biti asimetrično nagrađeni, ali će i puno izgubiti ako se pokaže da nisu u pravu. Pukovnici ili pokojnici. Po meni je to cilj zbog koga vredi rizikovati, pa i bankrotirati a cilj je da se centralno-bankarski kartel učini manje relevantnim.
Znaš i sam da fiat sistem ne može da preživi i izbegne imploziju bez konstantnog uvećanja mase novca u opticaju i zato se uopšte ne plašim za BTC i spavam mirno. BTC sigurno neće rasti istom brzinom kao prvih 15 godina ali moje očekivanje je svakako ubedljivo nadmašivanje svetske inflacije i obezvređivanja. Ne vidim kako sistem može da opstane bez novog QE kada god se on desi, u suprotnom imamo deflatornu spiralu.
Ne mora da bude zvanično sredstvo plaćanja, dovoljno da meni kao pojedincu služi za to dok god ima ljudi koji ga prihvataju, a ima ih puno. I da niko u tome ne može da nas spreči.
loldurrr: Ali i BTC je postao, u neku ruku, berzanska roba. Imaš market cap izražen u dolarima, koji je danas, npr. 2 triliona $, za mjesec dana 500 milijardi. Isto kao i dolar, samo volatilnije. Zato i kažem, da je to sve rezultat ponude i tražnje. Hipotetički, ja da imam milion BTC i odlučim to danas prodati, enormno ću oboriti cenu BTC. Ako je to valuta nezavisna od vanjskih uticaja - zašto će pasti toliko, kada imamo ograničenu količinu BTC-a. Svima je i dalje u podsvesti vrednost BTC izražena u USD, tako da je to isto kao i dinar, franak, akcija CocaCola i sl. Bar za sada...
A mogućnosti za korištenje BTC za robna plaćanja su mizerna. Ima li na vidiku mogućnosti da se vrednost nafte počne izražavati u BTC?
@BTCSRB: Meriti Bitkoin direktno prema robama i uslugama je itekako moguće i kada ga tako meriš, a ne prema fiat novcu, dugoročno cene gotovo svih roba i usluga padaju prema Bitkoinu. Cene svega izražene kroz BTC neće nestati ni u slučaju nestanka fiat novca, dolar sutra da prestane da postoji nikoga ne sprečava da izražava cene svega kroz BTC. Dolar i ostale valute nisu potrebni Bitkoinu.
Unlikely-Put-5524: Imam samo jedno pitanje za one "koji vide iza svega" i pronikli su bankarsku prevare da porobi čovečanstvo... Kako ne postoji mogućnost da je BTC i kripto nastao iz iste kuhinje i predstavlja ultimativni način za porobljavanje?
2% novčanika poseduje 95% svog BTC-a koji nije izgubljen. Znači da centralizacija može biti maksimalna...
@BTCSRB: Količina BTC-a u posedu ne daje kontrolu nad pravilima protokola i većinski vlasnici ne mogu da štampaju nove novčiće i tako uvećaju konačnu količinu u opticaju. Mogu samo da kratkoročno obore cenu i tako samo ostanu sa manje BTC-a koji imaju pošto će tržište vremenom apsorbovati te dampovane koine.
Unlikely-Put-5524: A mogu i dugoročno da obore cenu. Hajde da kažemo da imaš sada 10 BTC-a gde svaki vredi 40k
Veliki dumpu-ju ceo svoj bag u kontinutitetu kao što sad radi GS i posle godinu dana tvoj BTC sad vredi 4k, zašto misliš da bi ljudi nastavili da ga drže? Posebno ako znamo da ga 97% kupuje da bi zaradili, a ne zato što žele da ga koriste kao sredstvo plaćanja.
Ja bih ore BTC gledao kao commodity, jer sa svojim deflatornim svojstvima ne može biti valuta za plaćanje.
Takođe postoji i doomsday scenario gde jednostavno mogu svi da se dogovore da je ilegalan i to je onda to. Ovo mi deluje kao gotovo neverovatno, ali po meni je bilo koji maksimalizam potpuno detinjasto razmišljanje.
@BTCSRB: Pa padao je toliko puta za preko 70% i uvek se vraćao jer si uvek imao ljude koji su bili spremni da ga kupuju po bilo kojoj ceni, uključujući i mene. Pošto se ne može štampati, na kraju će ovi prodavci ostati bez BTC-a za prodaju i tržište apsorbovati čak i njihov "sell pressure". A ovi veliki koji drže tolike količine itekako dobro znaju vrednost toga što poseduju i nema smisla da svu količinu koju drže prodaju za inflatorni novac - prodavaće da bi finansirali svoj životni stil ili investiraju u biznise ili će ga koristiti kao kolateral za fiat pozajmice - ako raspolažu tolikim količinama i mogu da kontrolišu tržište nemaju strah da će im kolateral biti likvidiran.
Većina ljudi su fiat maksimalisti samim tim što su 100% u fiat novcu pa ne razmišljaju u pravcu doomsday scenarija kakav je upravo bila hiperinflacija devedesetih.
Romeo_y_Cohiba: Niko ti ne brani da ulažeš u bitcoin pod uslovom da znaš da je rizičniji od gotovog novca, štednje po viđenju, oročene štednje, obveznica, nekretnina, akcija, raznoraznih etfova, private equitya i derivata.
Drugim rečima ako ti je ok da danas uložiš 1000e, da za nedelju dana to vredi 500e, za mesec 1500 a za pola godina 300e ili 0 samo napred. Većini ljudi to nije ok.
Razlog zašto pamtimo Avrama je jer njegov dinar i dan danas koristimo. Prethodne uzastopne reforme nisu uspele kao što si i sam primetio.
Takođe, nije u pitanju "centralno-bankarska" prevara jer se ništa od toga ne bi desilo da ovom "odozgo" nisu zatrebale pare za finansiranje izvesnih stvari.
I dan danas, izvesni političar(i) izađu na TV i kažu da su "našli" novac za neki svoj genijalni plan i ljudi to puše. To u prevodu najčešće znači da će da nagna centralnu banku da mu doštampa novca i to nema veze sa bankama nego politikom..
@BTCSRB: Za investicione instrumente koje si naveo treba videti koliko su uspešno nadvladavali inflaciju prethodnih decenija i da li su očuvali kupovnu moć. Za štednju u banci i obveznice se i iz daleka vidi da nisu. US obveznice su u septembru imale drawdown od 48% od ATH iz 2020, a kao važe sa sigurnu investiciju. Čak i u momentu dospeća posle 10-30 godina jako teško čuvaju vrednost od inflacije.
A sada se zapitaj: da li zaista misliš da političari kontrolišu banke i bankare ili je možda obrnuto? Nisu političari ti koji su vlasnici krupnog kapitala.
Romeo_y_Cohiba: Ne investiraju svi na 10-30 godina za potrebe penzije. To je samo jedan od mnogo vidova i razloga investiranja. Nadvladavanje inflacije je isto tako samo jedan od kriterijuma. Samo pogledaš u šta jedan penzioni fond u SAD-u investira(hint: nije btc i nisu samo akcije). Npr. neki penzioni fondovi su od skoro počeli da investiraju u private equity ali isključivo do 15% veličine portfolija. Počeće i sa kriptom u nekom trenutku ali mogu da potpišem da će biti u još manjem procentu nego PE. Niko nije blesav da grune teško stečeni novac u nešto tako rizično osim u jako malim iznosima.
Ne znam ko koga kontroliše ali Avram je bio daleko manji baja od Slobe 90ih i pitao se za stvari samo u meri koliko mu je bio dozvoljeno da se pita. Ratovanje košta i finansira se štampanjem novca, nisu to neke neshvatljive stvari. Da ne pričam da smo bili pod apsolutnim sankcijama celog sveta.
Virtual_Plenty_6047: Npr jedan od velikih uspeha Japana od pre par decenija je zahvaljujući devalvaciji njihove valute, pa samim tim izvoz im je bio relativno jeftin. Naš dinar je jak, i to odgovara uvozničkom lobiju.
Nažalost mi ionako ništa ne proizvodimo tako da ne verujem da bi nešto pomoglo ako bi devalvirali dinar. Al svakako ovo je jedna viša ekonomija za koju naši političari nisu dorasli.
@BTCSRB: Gde je običan čovek u tom velikom japanskom uspehu? Postali su zemlja starih i nesrećnih mladih ljudi koji ne mogu da pobegnu iz "hamster wheel-a". Imaju "debt to GDP" od preko 260%. Taj dug nikada neće vratiti, a uz to će povući u ambis pola sveta jer najveći držaoci američkog duga - 14.5%. Spolja gladac, iznutra jadac. Iako je malo degutantno da mi iz Srbije komentarišemo Japance, opet pitam: gde je prosečan Japanac u celoj ovoj igri?
Why Japan Is Facing a Financial Disaster
Preporučujem da pogledate dokumentarac "Princes of the Yen | The Hidden Power of Central Banks" snimljenom po istoimenoj knjizi profesora Riharda Vernera koji je otac kvantitativnog popuštanja (quantitative easing) i ekspert za japansku ekonomiju i bankarski sistem.
Virtual_Plenty_6047: Zato sam rekao od pre nekoliko decenija. Jer su do pre nekih 30 godina bili 50 godina ispred celog sveta, sad su 20 godina iza naprednog sveta. Japanci su svako specifični. Poenta mog komentara da postoji razlog za neke zemlje da oslabe svoju valutu, i može itekako dobro da radi ako se radi u sinergiji sa nekim drugim ekonomskim merama. Tako da odgovor na to opet pitam, ne znam gde je prosečni Japanac, uskoro tamo trebam da idem pa ću ti reći. :'D
Odgledao sam ja ovaj dokumentarac odavno, super je. Pročitao mnoge knjige, a ponajviše od Austrijske ekonomske škole gde su pojedinci (Hayek) bili prvi koji su zagovarali novu decentralizovanu valutu, bili su u toj školi mnogi koji su prvi pričali o problemu inflacije i šta je tačno inflacija, ali su bili i za kapitalizam. Ali ovo je zaista jedna visoka ekonomija, videćeš da nije baš sve tako jednostavno kao što misliš.
Malo si previše u kriptovalutama pa gledaš na sve drugo u ekonomiji sa prekorom, pogotovu na kapitalizam. Evo i ja sam sam dobro investiran u kripto (uglavnom u BTC) pa sam itekako svestan da sve to može na kraju da bude potpuna pizdarija.
p.s. Knjiga za preporuku: 23 stvari koje vam ne kazu o kapitalizmu
@BTCSRB: Nisam u kriptovalutama nego isključivo u BTC.
Nisam ja protiv kapitalizma samo što nije pravi kapitalizam kada ne postoji slobodno tržište novca, pa samim tim ne postoji uopšte slobodno tržište koliko god se činilo tako. Kada su ekonomski subjekti prisiljeni da koriste određeni oblik novca, a monetarna politika se centralno planira - po meni tu nema slobodnog tržišta niti kapitalizma. Npr. formiranje cene Bitkoina i transakcionih naknada je čisto slobodno tržište jer tu nema "bailout-a", a BTC mining industrija je pravi primer slobodnog tržišta u kapitalizmu. Čista ponuda i potražnja bez intervencionizma. Ako si neprofitabilan nema ti spasa i bankrotiraćeš i nema nikoga ko će ti priteći u pomoć. Niko nije "too big to fail".
Znam da sam se ovde usredsredio usko na jednu industriju ali se može primeniti na celokupnu ekonomiju. Države i centralne banke su suvišne i apsolutno pokvare sve čega se dotaknu pa će u slučaju potpune pizdarije odgovornost biti na njima, a ne na Bitkoinu i njegovim držaocima.
kutija_keksa: Evo zašto btc nije pogodan kao valuta:
-Volatilna vrednost. Vrednost btc se menja i do 200% godišnje, dok dolar ne trpi inflaciju vecu od 10% godišnje (mada je u redovnim uslovima tipa 3%). Čak i dinar, ako gledaš realnu kupovnu moć u prodavnici nema volatilnost preko 30% na godišnjem nivou (jedno 7 puta nižu od BTC) Ako danas kupim BTC u vrednosti od 15 USD ne znam da li ću sutra moći da kupim 10 ili 20 USD za isti taj BTC.
-„Gas fees” koji se plaćaju na svaku transakciju, u poređenjusa kešom koji nema takvih problema.
-Spor transfer novca. Arhitektura blockchaina ne dozvoljava mreži da procesuira više od 10 transakcija po sekundi, što značida na transakciju možete čekati i po nekoloo sati, u poređenju sa kešom (bez odugovlačenja) ili debitnim karticama (10 sekundi do 10 minuta). Visa i MasterCard procesuiraju hiljadu puta više transakcija po sekundi.
-Retko ko eksplicitno prima BTC, tako da ćete plaćati menjačnici na kursu u oba smera, i pritom čekati menjačnicu.
-Podložan je manipulacijama velikih igrača poput Ilona Maska i velikih banki koje su u zadnjih pet godina debelo uložile u kripto. Fiat je na milosti države i njenih građana, dok je BTC na milost privatnih investitora. Kome verujete više?
-SVE BTC transakcije su jsvne, ako neko zna koji novčanik je vaš lako zna i koliko para ste kada slali kome, dok fizičke novčanice nemaju taj problem.
-Vrednost i upotreljivost BTC ne garantuje niko, dok vrednost i upotrebljivost fiat valute barem donekle garantuje država. Na primer, Srbija garantuje da je dinar upotrebljiv jer zahteva da vodu, struju, poreze, namete i takse plaćaš u dinarima, a i javni sektor (10% čitavog stanovništva) isplaćuje isključivo u dinarima.
OP očigledno ima jako ostrašćenu ideološku perspektivu... Ja nisam stručnjak, ali je moj otac pisao naučne radove o blockchainu dok je bio na doktorskim studijama, još kad je pomisao o BTC vrednijem od sto dolada bila smešna, tako da znam nešto malo kroz priče sa njim. Uostalom, sve o čemu pričam lako je proveriti pomoću javnih podataka. Ono što OP piše je jednim delom tačno, ali su iznete samo one informacije koje idu u prilog BTC.
Kripto kao pobuna protiv fiata, centralnih banaka i vlada je imao ideološke korene kod anarhista na internetu devedestih, međutim od njihovih belih papira i špekulacija dobili smo nešto što je kao valuta beskorisno. BTC može biti investicija, ako su ljudi iskreni sa sobom, ali ideja o valuti je prevaziđena. Ako i neka kripto valuta drži do toga onda je to Monero koji bar ima anonimnost.
@BTCSRB: Ne ulazeći u sve iznete navode taksativno, ipak moram da prokomentarišem neke od nepreciznih ili netačnih navoda.
Transakcione naknade kod Bitkoina se ne zovu "gas fees" već "transaction fees". Kod keša nema takvih problema ali ga ne možete poslati putem komunikacionog kanala bez posrednika. To mora da ima svoju cenu pošto BTC majneri moraju da imaju neki podsticaj da uključe nečiju transakciju u blok koji je ograničene veličine. BTC "fee market" je najslobodnije tržište na svetu. Fiat novac nemate mogućnost da pošaljete na daljinu bez posrednika koji takođe naplaćuje nekada dosta skupe naknade.
Besmisleno je porediti blokčejn kao "settlement layer" sa Visom i Mastercardom koje ne služe za finalno poravnanje. Glavni Bitkoin blokčejn se može pre uporediti s SWIFT-om ili FedWire-om kod kojih je jednom poravnata transakcija nepovratna, a Mastercard/Visa sa BTC "Lightning Network-om" koji služi za brza i jeftina plaćanja. Otac je trebalo da Vas nauči o Lightning mreži, kako funkcioniše i da je sposobna da procesuira više miliona transakcija u sekundi. Lightning mreža takođe nudi veći nivo privatnosti od glavnog blokčejna ali puno manju sigurnost.
Ne bih se složio da je fiat na milosti isključivo države i građana, samo ću spomenuti Crnu sredu iz septembra 1992. godine i spekulativni napad na britansku funtu.
BTC transakcije su javne ali su pseudonimne što znači da je jako teško utvrditi identitet ukoliko adresa nije povezana sa identitetom korisnika. Generisanje BTC adrese ne zahteva nikakvu identifikaciju ("krvnu sliku") za razliku od otvaranja bankovnog računa. Može se generisati neograničen broj adresa i na razne načine prekinuti i zamaskirati veza transakcija između njih radi očuvanja privatnosti. Ponovo, fizičke novčanice ne možemo slati putem komunikacionog kanala bez posrednika, podložne su konfiskaciji, uništenju i obezvređivanju.
Upotrebljivost Bitkoina garantuje "open source" kod, energija, matematika i kriptografija. To su mnogo jače garancije nego obećanja bilo koje države koja su toliko puta u istoriji izigrale poverenje sopstvenog stanovništva - poput Jugoslavije devedesetih.
Ja sam BTC spomenuo kao potencijalno rešenje za (hiper)inflaciju tek u kraćem delu na kraju teksta, a od Vas i od ostalih komentatora sam dobio nesrazmeran odgovor usmeren na Bitkoin, a puno manje usmeren na navode iz najvećeg dela posta.
Tako ste i vi izneli isključivo informacije koje ne idu u prilog BTC-a, a potpuno ignorisali sve očigledne nedostatke fiat novca (kako u fizičkom, tako i u digitalnom obliku) koji su se i ispoljili tokom hiperinflacije devedesetih, a ispoljavaju se i dan-danas.
Svako dobro!
kutija_keksa: Zato su i „Gas fees” pod navodnicima.
Ne vidim zašto bi bilo dobro imati „slobodno tržište” kada se radi o kopačima.
Ali, čak i da je dobro imati slobodno tržište, morate primetiti da BTC kopanje nije tako slobodno. Postojanje ASIC mašina znači da se kopanje prevashodno isplati velikim igračima (ne mislim na likove sa 3 riser kartice u PC, nego na kineze sa skladištima teških preko milion u opremi). Takođe, te velike operacije organi vlasti mogu zaustaviti kad im se prohte (Kina).
Jako je teško izvući BTC anonimno bez gubitka kod menjača -- pojedinca ili non KYC institucije.
Što se upotrebljivosti BTC tiče, šta meni garantuje da ću imati na šta da potrošim BTC? To je ključno pitanje. A kasa Jugoslovenski fiat nije bio upotebljiv, vidim da Nemački jeste. Isto tako, mislim da će USD biti upotrebljiv dugo, a kada USD bude neupotrebljiv društvo će ionako biti u apokalipsi gde papir nije važan koliko i hrana, utočište, voda, radio, municija, lekovi i vatreno oružje.
Naravno da iznosim samo informacije koje proizilaze iz nedostataka, to je balans postu i komentarima. Da su ljudi samo blatili kripto moj komentar bi mnogo više ličio na originalni post nego na moj prošli komentar. Ja se sa mnogim tvrdnjama u postu slažem delimično ili potpuno, samo želim da pružim kontekst za tumačenje toga.
Ideološki su mi Cryptopunks potpuno zanimljivi, ali cinizam je opravdan kada se u obzir uzme priča. Ljudi su želeli da se odupru bankama, vladama, kontroli i prismotri. Izmislili su tehnologiju. Počeli su da koriste i popularizuju tu tehnologiju. U prostor su ušle banke i vlade, kupovanjem, prodajom i praćenjem samog tržišta (danas sve velike menjačnice imaju KYC procedure). Kao u matriksu, kontrolisana opozicija. Ok, ovo je lična teorija zavere u koju ni ja ne verujem u potpunosti.
Ako govorimo o crypto kao valuti mislim da je XMR mnogo bolja VALUTA od BTC, dok je mnogo gora investicija. Jednostavno se slažem sa političkim i ideološkim ciljevima pionira kripto valuta, ali smatram da su oni ogromnim delom iznevereni zbog ulaska banaka i država u celu priču, te njihova stara rešenja više ne rešavaju originalne probleme.
@BTCSRB: BTC kao neutralni novac je za svakoga, pa i za bankare i države. Ne možemo ih sprečiti da ga kupe na tržištu i stave ga u kakav god instrument, pa i ETF. Ne možemo ih sprečiti da ga konfiskuju od onih koji nisu dobro obezbedili svoje ključeve. Države su regulisale ono što su mogle, poput menjačnica, kroz AML/KYC procedure ali kakve to veze ima sa BTC-om? Na protokol kao protokol nisu mogle da utiču.
Ko želi i dalje može koristiti BTC kako je i prvobitno predviđeno - za p2p transakcije i skladištenje vrednosti u "self custody-u". Bitkoin je i dalje "bearer asset" otporan na cenzuru i konfiskaciju. Ne vidim da je taj pravac promenjen samo zato što su ušle banke i države. Možda nije u duhu Bitkoina da ga kupuju fondovi pa ga prodaju upakovanog u ETF. Najmanje je u duhu bitkoina da se nekome zabrani da ga kupuje.
Kako to mislite "ne vidite zašto bi bilo dobro imati „slobodno tržište” kada se radi o kopačima? Na decentralizaciji mininga se radi (StratumV2 protkol, Ocean pool...), a kineski primer je samo pokazatelj koliko je otporno: nakon zabrane raširilo se dodatno po svetu, a u Kini se i dalje nalazi 21% hešrejta. Majneri imaju veoma male margine profita zbog same prirode rudarenja i halvinga pa će bilo kakav "fck around" poput cenzure transakcija verovatno značiti bankrot.
Možemo do sutra pričati o XMR vs BTC i navešću puno razloga zašto XMR ne može i neće zaživeti kao novac, a pre svega je manjak decentralizacije (neograničena veličina blokčejna) i otpornost na državni napad - sve što Bitkoin ima. Kada je novac u pitanju pobednik nosi sve i tu je Monero već izgubio, dok će BTC poboljšanu privatnost obezbediti na ostalim nivoima, sidechainovima itd (Lightning, Liquid, Cashu, Fedimint, Ark i ko zna šta sve što još i ne postoji - nivo developmenta u Bitkoin prostoru je ogroman).
Dolar će uvek u nekom obliku biti upotrebljiv ali ne znači da će zauvek ostati svetska rezervna valuta, kao što i danas postoji funta ali odavno nije više ono što je bila na vrhuncu Britanske imperije.
kutija_keksa: Pa ti protokoli sprečavaju pljude da anonimno kupe BTC.
Mislim, BTC realno ima neku primenu, ali ja ga danas npr. imam čisto kao neku malu investicijicu, i to još od doba kad je kopanje sa 2 grafičke u kućnom PC bilo isplativo po skupoj struji. Ali BTC prosto nije dobra alternativa fizičkom novcu na nivou države zbog volatilnosti i manjka kontrole. Jedna ogromna poluga države je puštanje u promet novog novca, i tako se kontroliše inflacija, pored menjanja kamatnih stopa. Bez mogućnosti štampe gubi se i taj faktor kontrole. A inflacija od 2-3% godišnje je zdrava, dok je za ekonomiju deflacija (kojoj je BTC bar delimično sklon) haos, jer smanjuje ekonomsku aktivnost i investicije...
Što se tiče državnog napada na XMR, misliš na to kako jedna država može da realistično sprovede 51% napad?
XMR nije vrhovna valuta ali meni se sviđa kako za njega nema ASIC mašina, kako je anoniman u smislu da ne možeš lako da provališ ko kome koliko i kada šalje šta... Mislim da će XMR sigurno u toj privacy niši zameniti neka druga valuta kroz 10-15 godina koja ima bolji algoritam i tehnologiju...
Dobra dosetka za veličinu blockchaina, ali ona je trenutno 160GB cela / 50 GB pruned, tako nešto. Sve dok nije preko 10TB (100x) veća može je pohraniti najveći hard disk namenjen „običnim ljudima”, a kad se dođe do tad verovatno će i cene tih diskova biti pristupačnije nego danas. Sa druge strane, agresivan pruning je takođe opcija. A da ne govorimo o sidechainovima koji takođe postoje za XMR.
Da, to za dolar je i moja poenta, nekako će biti upotrebljiv uvek, dok je kripto neupotrebljiv bez neta, a i nema mnogo šta da se kupi kriptom u poređenju sa fiatom. I
@BTCSRB: Ima bezbroj načina da se nabavi non-KYC Bitkoin: coinjoin, coinmixing, rudarenje u non-KYC pulu, nabavka nekog drugog kripta putem KYC menjačnice pa "trustless atomic swap" za BTC, nabavka KYC BTC-a putem Lightning-a pa "submarine swap" on-chain, zatim nabavka bilo kog KYC kripta ili Lightning ili on-chain BTC-a pa swap na sidechain Liquid BTC gde su transakcije tajne slično XMR-u i nazad swap na on-chain. Naravno i stara narodska razmena na ulici. XMR se isto može koristiti za svrhu nabavke non-KYC Bitkoina. U svim ovim slučajevima se adrese koje su krajnje destinacije tih sredstava ne mogu ili jako teško povezati sa KYC identitetom korisnika. Više na: kycnot.me
Diskusija o tome da li je zdrava i potrebna inflacija i da li je uopšte potreban državni intervencionizam u ekonomiji je stara diskusija između Kejnzijanske i Austrijske ekonomske škole. Po meni svaka inflacija je pljačka. Da ne govorimo da centralni bankari ne snose nikakvu odgovornost za gubitak kontrole nad inflacijom koji se meri u stotinama procenata "omaška" jer kada je ciljana inflacija 2%, a imamo inflaciju od 10% to je onda promašaj od 500%. A svi vodeći centralni bankari su i dalje na svojim funkcijama od početka inflacije negde 2020. godine iako su izneverili sva očekivanja. Nisu izabrani od strane naroda i nemoguće ih je smeniti od strane naroda, a utiču na živote svih!
Usled tehnološkog napretka i rasta produktivnosti, prirodno stanje slobodnog tržišta je pad cena, a ne njihov konstantan rast kroz inflaciju. Ne postoji nikakva "poželjna" ili "neophodna" inflacija, svaka "ciljana" inflacija je pljačka koji onemogućava populaciju da uživa u plodovima sopstvene produktivnosti u obliku nižih cena svih roba i usluga. Bitkoin zbog svoje fiksne ponude novca u opticaju (21 milion novčića = apsolutna digitalna oskudnost) nameće ovu disciplinu slobodnog tržišta i tehnološkog napretka. Dok je postojeći dužnički fiat sistem dizajniran da krade plodove produktivnosti, Bitkoin omogućava populaciji da ih zadrži u obliku nižih cena.
Kada nema rasta cena, inflacija je 0% i cene su stabilne. Krađa i tada postoji, jer cene prirodno padaju zbog povećanja efikasnosti proizvodnje/usluga, gde bi se tada veca količina robe/usluga, takmičila za istu (fiksnu) količinu novča od 21M BTC-a.
Kakav je ishod ove diskusije nije bitno, bitno je da sada svako ima slobodu izbora kakav novac želi da koristi a ne da bude prisiljen da koristi isključivo inflatorni novac. Ako se neko ne slaže sa modernom monetarnom teorijom, sada ima alternativu koju nekada nije imao (zlato je odavno izgubilo bitku sa MMT) pre postojanja Bitkoina.
kutija_keksa: Neki od ovih non kyc nacina su mi vec bili poznati, neki nisu, ovo je bas informativan komentar.
A što je inflacija pljačka? Bez obzira na inflaciju, broj novčanica u novčaniku ostaje isti, to što se one sada mogu zameniti za manje robe je druga priča. Da li je onda i zlato pljačka, jer neko kupi, na primer, 100g zlata danas, a sutra na tržištu cena zlata padne? Da li je onda pljačka i BTC, jer i danas i kad je BTC bio na vrhuncu cene imam isti broj satoshija, samo je danas njihova vrednost manja?
Ne vidim zašto bi centralni bankari snosili odgovornost zbog inflacije. Oni ugrobo imaju dve poluge za kontrolu inflacije: kamatne stope i štampanje novca. U realnosti na inflaciju utiče mnogo faktora na koje centralna banka nema uticaj, niti koje može da predvidi: pandemije, ratovi, državni budžeti i zaduživanja, trgovina u datoj valuti (i izvoz i uvoz), porast i pad produktivnosti... Oni imaju donekle uticaj, ali nisu svemoćni.
Što se tiče izbora, ovo već zalazi u politiku a ne u finansije, ali ni direktor pošte, ni direktor EPS, ni direktor vodovoda nisu birani na izborima na kojima glasaju svi, a utiču na živote svih!
Ne verujem u kripto kao spasioce kapitalizma ili pojedinca. Ovo je sada više politički, ali zaista mislim da u kapitalizmu prosečna osoba nema slobode, a da je kripto u najbolju ruku jedna mala stavka koja omogućava skladištenje stečenog kapitala (ovo se dobija ako prihvatimo sve kripto pozitivne teze), ali ne rešava problem radnika koji čine 95% društva i doprinose 99% vrednosti a kapitala kontrolišu višestruko manje.
Otkud znam, ono, da rezimiram: kripto je koristan alat koji još nije dostigao svoj vrhunac, ali neće nešto mnogo promeniti svet. To je neko moje viđenje.
@BTCSRB: Kako nije pljačka? Broj novčanica u novčaniku ostaje isti ali ukupan broj novca u opticaju se uvećava i tako obezvređuje tvoje novčanice. Inače, znaš vrlo dobro da fizički keš čini manje od 10% ukupnog novca u opticaju, a ostalo je digitalno. Dakle "money supply" se uvećava pritiskom na dugme tastature računara u FED/ECB/NBS... Neko stvara novac ni iz čega za koji svi moramo da radimo trošeći svoje dragoceno i ograničeno vreme na ovom svetu. Tako nam efektivno krade vreme pošto tvoj radni sat iz prošlosti konstantno može da kupi manje roba i usluga u budućnosti, a zbog tehnološkog napretka i rasta produktivnosti bi realno cene trebaju da budu niže vremenom
Kako možeš da porediš fiat, zlato i BTC u tom smislu? Vrednost fiata prevashodno smanjuje ljudska manipulacija sa strane ponude koja se uvek uvećava, dok je potražnja permanentno rastuća zbog zakona o "legal tenderu" i rasta privrede i broja stanovnika. Ovo sa BTC je strana potražnje koju reguliše slobodno tržište dok ukupna ponuda nije podložna ljudskoj manipulaciji. Dugoročno, vrednost zlata i BTC raste sa rastućom potražnjom jer nema manipulacije ponude.
Centralni bankari će optužiti sve druge faktore da bi skrenuli pažnju sa svoje odgovornosti za inflaciju, a za ratove se može reći da su čak i saučesnici pošto tokovi novca mogu utvrditi veoma zanimljivu vezu između njih i vojno-industrijskog kompleksa. Na stranu to, dolarska monetarna masa je samo između februara i aprila 2020. uvećana za 1.39 biliona/triliona što je više nego ukupna monetarna masa iz 2008-09 krize. U krizi 2008-09 su od septembra 2008. do januara 2009. naštampali 803 milijarde i tako uvećali monetarnu masu za 88% sa 909 milijardi na 1712 milijardi - to znači da su 4 meseca naštampali skoro isto novca kao tokom celih 95 prethodnig godina sopstvenog postojanja Federalnih rezervi. Te 2020. su i potpuno ukinuli obavezne rezerve u komercijalnim bankama.
ECB je naštampala 1T evra "zbog kovida". A kao naštampali su jer je bila zatvorena celokupna privreda, pa što ste tako agresivno zatvarali privredu - trebalo je da pustite ljude da rade a ne da se igrate Mao Ce Tunga. I uprkos nezapamćenom štampanju ti isti centralni bankari su nazivali inflaciju "prolaznom" - dakle ni zrnce odgovornosti.
Ako u kapitalizmu prosečna osoba nema slobode, šta reći za komunizam gde ne da nema slobode nego nema ni života pošto su komunistički režimi pobili na desetine miliona ljudi?
Na hipotetičkom BTC standardu zbog fiksne količine novca u opticaju bi se popravio položaj radnika jer kapitalisti ne mogu da beskonačno uvećavaju svoj BTC kapital i kupovna moć i radnika i kapitalista bi procentualno podjednako rasla i običan radnik bi imao mnogo bolje šanse da i sam postane kapitalista nego danas. Imao bi mogućnost da štedi od svoje plate jer mu novac ne bi gubio vrednost i u nekom trenutku bi iz svoje štednje finansirao neki biznis, a ne zaduživanjem. Tako bi se ravnomernije rasporedilo društveno bogatstvo ali ne centralnim planiranjem nego kroz slobodno tržište.
-
 @ 58537364:705b4b85
2025-05-24 20:48:43
@ 58537364:705b4b85
2025-05-24 20:48:43“Any society that sets intellectual development as its goal will continually progress, without end—until life is liberated from problems and suffering. All problems can ultimately be solved through wisdom itself.
The signpost pointing toward ‘wisdom’ is the ability to think—or what is called in Dhamma terms, ‘yoniso-manasikāra,’ meaning wise or analytical reflection. Thinking is the bridge that connects information and knowledge with insight and understanding. Refined or skillful thinking enables one to seek knowledge and apply it effectively.
The key types of thinking are:
- Thinking to acquire knowledge
- Thinking to apply knowledge effectively In other words, thinking to gain knowledge and thinking to use that knowledge. A person with knowledge who doesn’t know how to think cannot make that knowledge useful. On the other hand, a person who thinks without having or seeking knowledge will end up with nothing but dreamy, deluded ideas. When such dreamy ideas are expressed as opinions, they become nonsensical and meaningless—mere expressions of personal likes or dislikes.
In this light, the ‘process of developing wisdom’ begins with the desire to seek knowledge, followed by the training of thinking skills, and concludes with the ability to express well-founded opinions. (In many important cases, practice, testing, or experimentation is needed to confirm understanding.)
Thus, the thirst for knowledge and the ability to seek knowledge are the forerunners of intellectual development. In any society where people lack a love for knowledge and are not inclined to search for it, true intellectual growth will be difficult. That society will be filled with fanciful, delusional thinking and opinions based merely on personal likes and dislikes. For the development of wisdom, there must be the guiding principle that: ‘Giving opinions must go hand-in-hand with seeking knowledge. And once knowledge is gained, thinking must be refined and skillful.’”
— Somdet Phra Buddhaghosacariya (P.A. Payutto) Source: Dhamma treatise “Organizing Society According to the Ideals of the Sangha”
Note: “Pariyosāna” means the complete conclusion or the final, all-encompassing end.
“We must emphasize the pursuit of knowledge more than merely giving opinions. Opinions must be based on the most solid foundation of knowledge.
Nowadays, we face so many problems because people love to express opinions without ever seeking knowledge.”
— Somdet Phra Buddhaghosacariya (P.A. Payutto)
-
 @ 3283ef81:0a531a33
2025-05-24 18:12:47
@ 3283ef81:0a531a33
2025-05-24 18:12:47Lorem ipsum dolor sit amet, consectetur adipiscing elit\ enean magna lorem, dignissim et nisl a, iaculis eleifend dolor
uspendisse potenti
-
 @ bf47c19e:c3d2573b
2025-05-24 17:11:28
@ bf47c19e:c3d2573b
2025-05-24 17:11:28Originalni tekst na bitcoin-balkan.com.
Pregled sadržaja
- Odakle Potiče Bitcoin?
- Koje Probleme Rešava Bitcoin?
- Kako se Bitcoin razvijao u poslednjoj deceniji?
Bitcoin je peer to peer elektronski keš, novi oblik digitalnog novca koji se može prenositi između ljudi ili računara, bez potrebe za učestvovanjem pouzdanog posrednika (kao što je banka) i čije izdavanje nije pod kontrolom nijedne stranke.
Zamislite papirni dolar ili metalni novčić. Kad taj novac date drugoj osobi, ona ne mora da zna ko ste vi.
On samo treba da veruju da novac koji dobiju od vas nije falsifikat. Obično, proveravanje falsifikata „fizičkog“ novca, ljudi rade koristeći samo oči i prste ili koristeći specijalnu opremu za testiranje ukoliko se radi o značajnijoj sumi novca.
Većina plaćanja u našem digitalnom društvu vrši se putem Interneta korišćenjem neke posredničke usluge: kompanije za izdavanje kreditnih kartica poput Visa, snabdevača digitalnih plaćanja kao što je PayPal ili Apple Pay ili mrežne platforme poput WeChat u Kini.
Kretanje ka digitalnom plaćanju sa sobom donosi oslanjanje na nekog centralnog aktera koji mora odobriti i verifikovati svaku uplatu.
Priroda novca se promenila od fizičkog predmeta koji možete da nosite, prenesete i autentifikujete do digitalnih bitova koje mora da čuva i verifikuje treća strana koja kontroliše njihov prenos.
Odricanjem od gotovine u korist „udobnih“ digitalnih plaćanja, mi takođe stvaramo sistem u kome dajemo ogromna ovlašćenja onima koji bi poželeli da nas tlače.
Platforme za digitalno plaćanje postale su osnova distopijskih autoritarnih metoda kontrole, poput onih koje kineska vlada koristi za nadgledanje disidenata i sprečava građane, čije ponašanje im se ne svidja, da kupuju robu i plaćaju usluge.
Bitcoin nudi alternativu centralno kontrolisanom digitalnom novcu sa sistemom koji nam vraća prirodu korišćenja keša – čovek čoveku, ali u digitalnom obliku.
Bitcoin je digitalno sredstvo koje se izdaje i prenosi preko mreže međusobno povezanih računara, od koji svaki od njih samostalno potvrđuje da svi ostali igraju po pravilima.

Bitcoin Mreža
Odakle Potiče Bitcoin?
Bitcoin je izumela osoba ili grupa poznata pod pseudonimom Satoshi Nakamoto, oko 2008. godine.
Niko ne zna Satoshijev identitet, a koliko znamo, oni su nestali i o njima se godinama ništa nije čulo.
11.februara 2009. godine, Satoshi je pisao o ranoj verziji Bitcoin-a na mrežnom forumu za cypherpunkere, ljude koji rade na tehnologiji kriptografije i koji su zabrinuti za privatnost i slobodu pojedinca.
Iako ovo nije prvo zvanično objavljivanje Bitcoin-a, sadrži dobar rezime Satoshi-jevih motiva.
Razvio sam novi P2P sistem e-keša otvorenog koda pod nazivom Bitcoin. Potpuno je decentralizovan, bez centralnog servera ili pouzdanih stranki, jer se sve zasniva na kripto dokazima umesto na poverenju. […]
Osnovni problem konvencionalne valute je potpuno poverenje koje je potrebno za njeno funkcionisanje. Centralnoj banci se mora verovati da neće devalvirati valutu, ali istorija tradicionalnih valuta je puna primera kršenja tog poverenja. Bankama se mora verovati da drže naš novac i prenose ga elektronskim putem, ali one ga daju u talasima kreditnih balona sa delićem rezerve. Moramo im verovati sa našom privatnošću, verovati im da neće dozvoliti da kradljivci identiteta pokradu naše račune. Njihovi ogromni režijski troškovi onemogućavaju mikro plaćanja.
Generaciju ranije, višekorisnički time-sharing računarski sistemi imali su sličan problem. Pre pojave jake enkripcije, korisnici su morali da imaju pouzdanje u zaštitu lozinkom kako bi zaštitili svoje fajlove […]
Tada je jaka enkripcija postala dostupna širokim masama i više nije bilo potrebno poverenje. Podaci bi se mogli osigurati na način koji je fizički bio nemoguć za pristup drugima, bez obzira iz kog razloga, bez obzira koliko je dobar izgovor, bez obzira na sve.
Vreme je da imamo istu stvar za novac. Uz e-valutu zasnovanu na kriptografskom dokazu, bez potrebe da verujete posredniku treće strane, novac može biti siguran i transakcije mogu biti izvršene bez napora. […]
Rešenje Bitcoin-a je korišćenje peer-to-peer mreže za proveru dvostruke potrošnje. Ukratko, mreža radi poput distribuiranog servera vremenskih žigova, obeležavajući prvu transakciju koja je potrošila novčić. Potrebna je prednost prirode informacije koju je lako širiti, ali je teško ugušiti. Za detalje o tome kako to funkcioniše, pogledajte članak o dizajnu na bitcoin.org
Satoshi Nakamoto
Koje Probleme Rešava Bitcoin?
Razdvojimo neke od Satoshi-jevih postova kako bismo uvideli razloge njegove motivacije.
„Razvio sam novi P2P sistem e-keša otvorenog koda.“
P2P je skraćenica za peer to peer i ukazuje na sistem u kojem jedna osoba može da komunicira sa drugom bez ikoga u sredini, kao medjusobno jednaki.
Možete se setiti P2P tehnologija za razmenu datoteka poput Napster-a, Kazaa-e i BitTorrrent-a, koje su prve omogućile ljudima da dele muziku i filmove bez posrednika.
Satoshi je dizajnirao Bitcoin kako bi omogućio ljudima da razmenjuju e-keš, elektronski keš, bez prolaska preko posrednika na približno isti način.
Softver je otvorenog koda, što znači da svako može videti kako funkcioniše i doprineti tome.
Ne treba da verujemo ni u šta što je Satoshi napisao u svom postu o tome kako softver radi.
Možemo pogledati kod i sami proveriti kako to funkcioniše. Štaviše, možemo promeniti funkcionalnost sistema promenom koda.
„Potpuno je decentralizovan, bez centralnog servera ili pouzdanih stranki …“
Satoshi napominje da je sistem decentralizovan kako bi se razlikovao od sistema koji imaju centralnu kontrolu.
Prethodne pokušaje stvaranja digitalne gotovine poput DigiCash-a od strane Davida Chaum-a podržavao je centralni server, računar ili skup računara koji je bio odgovoran za izdavanje i verifikaciju plaćanja pod kontrolom jedne korporacije.
Takve, centralno kontrolisane privatne šeme novca, bile su osuđene na propast; ljudi se ne mogu osloniti na novac koji može nestati kada kompanija prestane sa poslovanjem, bude hakovana, pretrpi pad servera ili je zatvori vlada.
Bitcoin održava mreža pojedinaca i kompanija širom sveta.
Da bi se Bitcoin isključio, bilo bi potrebno isključiti desetine do stotine hiljada računara širom sveta u isto vreme, zauvek, od kojih su mnogi na nepoznatim lokacijama.
Bila bi to beznadežna igra, jer bi svaki napad ove prirode jednostavno podstakao stvaranje novih Bitcoin čvorova ili računara na mreži.
„… sve se zasniva na kripto dokazima umesto na poverenju“
Internet, a u stvari i većina savremenih računarskih sistema, izgrađeni su na kriptografiji, metodi prikrivanja informacija, tako da je može dekodirati samo primalac informacije.
Kako se Bitcoin oslobađa potrebe za poverenjem? Umesto da verujemo nekome ko kaže „Ja sam Alisa“ ili „Imam 10 $ na računu“, možemo koristiti kriptografsku matematiku da bismo izneli iste činjenice na način koji je vrlo lako verifikovati od strane primaoca dokaza ali ga je nemoguće falsifikovati.
Bitcoin u svom dizajnu koristi kriptografsku matematiku kako bi učesnicima omogućio da provere ponašanje svih ostalih učesnika, bez poverenja u bilo koju centralnu stranku.
„Moramo im verovati [bankama] sa našom privatnošću, verovati im da neće dozvoliti da kradljivci identiteta pokradu naše račune“
Za razliku od korišćenja vašeg bankovnog računa, sistema digitalnog plaćanja ili kreditne kartice, Bitcoin omogućava dvema stranama da obavljaju transakcije bez davanje bilo kakvih ličnih podataka.
Centralizovana skladišta potrošačkih podataka koji se čuvaju u bankama, kompanijama sa kreditnim karticama, procesorima plaćanja i vladama, predstavljaju pravu poslasticu za hakere.
Kao dokaz Satoshi-jeve poente služi primer iz 2017. godine kada je Equifax masovono kompromitovan, kada su hakeri ukrali identifikacione i finansijske podatke za više od 140 miliona ljudi.
Bitcoin odvaja finansijske transakcije od stvarnih identiteta.
Na kraju krajeva, kada nekome damo fizički novac, on nema potrebu da zna ko smo, niti treba da brinemo da će nakon naše razmene moći da iskoristi neke informacije koje smo mu dali da ukrade još našeg novca.
Zašto ne bismo očekivali isto, ili čak i bolje, od digitalnog novca?
„Centralnoj banci se mora verovati da neće devalvirati valutu, ali istorija tradicionalnih valuta je puna primera kršenja tog poverenja.“
Pojam tradicionalna valuta, odnosi se na valutu izdatu od strane vlade i centralne banke, koju vlada proglašava zakonskim sredstvom plaćanja.
Istorijski, novac je nastao od stvari koje je bilo teško proizvesti, koje su bile lake za proveravanje i transport, poput školjki, staklenih perli, srebra i zlata.
Kad god bi se nešto koristilo kao novac, postojalo je iskušenje da se stvori više toga.
Ako bi neko pronašao vrhunsku tehnologiju za brzo stvaranje velike količine nečega, ta stvar bi izgubila vrednost.
Evropski naseljenici uspeli su da liše afrički kontinent bogatstva trgujući staklenim perlicama koje su se lako proizvodile za ljudske robove.
Isto se dogodilo sa američkim indijancima, kada su kolonisti otkrili način brze proizvodnje vampum školjki, koje su starosedeoci smatrali retkim.
Vremenom, širom sveta ljudi su shvatili da je samo zlato dovoljno retko da deluje kao novac, bez straha da bi neko drugi mogao da ga stvori u velikim količinama.
Polako smo prešli sa svetske ekonomije koja je koristila zlato kao novac na onu gde su banke izdavale papirne sertifikate kao dokaz posedovanja tog zlata.
Nixon je okončao međunarodnu konvertibilnost američkog dolara u zlato 1971. godine, privremenim rešenjem, koje je ubrzo postalo trajno.
Kraj zlatnog standarda omogućio je vladama i centralnim bankama da imaju punu dozvolu da povećavaju novčanu masu po svojoj volji, razredjujući vrednost svake novčanice u opticaju, poznatije kao umanjenje vrednosti.
Iako je izdata od strane vlade, suštinska tradicionalna valuta je novac koji svi znamo i svakodnevno koristimo, ipak je relativno novo iskustvo u opsegu svetske istorije.
Moramo verovati našim vladama da ne zloupotrebljavaju njegovo štamparije, i ne treba nam puno muke da nadjemo primere kršenja tog poverenja.
U autokratskim i centralno planiranim režimima gde vlada ima prst direktno na mašini za novac, kao što je Venecuela, valuta je postala gotovo bezvredna.
Venecuelanski Bolivar prešao je sa 2 bolivara za 1 američki dolar, koliko je vredeo 2009. godine, na 250.000 bolivara za 1 američki dolar 2019. godine.

Pogledajte koliko novčanica je bilo potrebno za kupovinu piletine u Venecueli posle hiperinflacije.

Satoshi je želeo da ponudi alternativu tradicionalnoj valuti čija se ponuda uvek nepredvidivo širi.
Da bi sprečilo umanjenje vrednosti, Satoshi je dizajnirao novčani sistem gde je zaliha bila fiksna i izdavana po predvidljivoj i nepromenjivoj stopi.
Postojaće samo 21 milion Bitcoin-a.
Međutim, svaki Bitcoin se može podeliti na 100 miliona jedinica koje se sada nazivaju satoshis (sats-ovi), što će činiti ukupno 2,1 kvadriliona satoshi-a u opticaju oko 2140. godine.

Pre Bitcoin-a nije bilo moguće sprečiti beskrajnu reprodukciju digitalnih sredstava.
Kopirati digitalnu knjigu, audio datoteku ili video zapis i poslati ga prijatelju, je jeftino i lako.
Jedini izuzeci od toga su digitalna sredstva koja kontrolišu posrednici.
Na primer, kada iznajmite film sa iTunes-a, možete ga gledati na vašem uređaju samo zato što iTunes kontroliše distribuciju tog filma i može ga zaustaviti nakon perioda njegovog iznajmljivanja.
Slično tome, vaša banka kontroliše vaš digitalni novac. Zadatak banke je da vodi evidenciju koliko novca imate.
Ako ga prenesete nekom drugom, oni će odobriti ili odbiti takav prenos.
Bitcoin je prvi digitalni sistem koji sprovodi oskudicu bez posrednika i prvo je sredstvo poznato čovečanstvu čija je nepromenljiva ponuda i raspored izdavanja poznat unapred.
Ni plemeniti metali poput zlata nemaju ovo svojstvo, jer uvek možemo iskopati sve više i više zlata ukoliko je to isplativo.
Zamislite da otkrijemo asteroid koji sadrži deset puta više zlata nego što ga imamo na zemlji.
Šta bi se dogodilo sa cenom zlata uzimajući u obzir tako obilnu ponudu? Bitcoin je imun na takva otkrića i manipulisanje nabavkom.
Jednostavno je nemoguće proizvesti više od toga (21 miliona).
„Podaci bi se mogli osigurati na način koji je fizički bio nemoguć za pristup drugima, bez obzira iz kog razloga, bez obzira koliko je dobar izgovor, bez obzira na sve. […] Vreme je da imamo istu stvar za novac “
Naše trenutne metode obezbeđivanja novca, poput stavljanja u banku, oslanjaju se na poverenje nekome drugom da će obaviti taj posao.
Poverenje u takvog posrednika ne zahteva samo sigurnost da on neće učiniti nešto zlonamerno ili glupo, već i da vlada neće zapleniti ili zamrznuti vaša sredstva vršeći pritisak na ovog posrednika.
Međutim, videli smo bezbroj puta da vlade mogu, i zaista uskraćuju pristup novcu kada se osećaju ugroženo.
Nekom ko živi u Sjedinjenim Državama ili nekoj drugoj visoko regulisanoj ekonomiji možda zvuči glupo da razmišlja da se probudi sa oduzetim novcem, ali to se događa stalno.
PayPal mi je zamrzao sredstva jednostavno zato par meseci nisam koristio svoj račun.
Trebalo mi je više od nedelju dana da vratim pristup „svom“ novcu.
Srećan sam što živim u Europi, gde bih se bar mogao nadati da ću potražiti neko pravno rešenje ako mi PayPal zamrzne sredstva i gde imam osnovno poverenje da moja vlada i banka neće ukrasti moj novac.
Mnogo gore stvari su se dogodile, i trenutno se dešavaju, u zemljama sa manje slobode.
Banke su se zatvorile tokom kolapsa valuta u Grčkoj.
Banke na Kipru su koristile kaucije da konfiskuju sredstva od svojih klijenata.
Indijska vlada je proglasila određene novčanice bezvrednim.
Bivši SSSR, u kojem sam odrastao, imao je ekonomiju pod kontrolom vlade što je dovelo do ogromnih nestašica robe.
Bilo je nezakonito posedovati strane valute kao što je američki dolar.
Kada smo poželeli da odemo, mojoj porodici je bilo dozvoljeno da zameni samo ograničenu količinu novca po osobi za američke dolare po zvaničnom kursu koji je bio u velikoj meri različit od pravog kursa slobodnog tržišta.
U stvari, vlada nam je oduzela ono malo bogatstva koje smo imali koristeći gvozdeni stisak na ekonomiji i kretanju kapitala.
Autokratske zemlje imaju tendenciju da sprovode strogu ekonomsku kontrolu, sprečavajući ljude da na slobodnom tržištu povuku svoj novac iz banaka, iznesu ga iz zemlje ili da ga razmene u ne još uvek bezvredne valute poput američkog dolara.
To omogućava vladinoj slobodnoj vladavini da primeni sulude ekonomske eksperimente poput socijalističkog sistema SSSR-a.
Bitcoin se ne oslanja na poverenje u treću stranu da bi osigurao vaš novac.
Umesto toga, Bitcoin onemogućava drugima pristup vašim novčićima bez jedinstvenog ključa koji imate samo vi, bez obzira iz kog razloga, bez obzira koliko je dobar izgovor, bez obzira na sve.
Držeći Bitcoin, držite ključeve sopstvene finansijske slobode. Bitcoin razdvaja novac i državu
„Rešenje Bitcoin-a je korišćenje peer-to-peer mreže za proveru dvostruke potrošnje […] poput distribuiranog servera vremenskih žigova, obeležavajući prvu transakciju koja je potrošila novčić“
Mreža se odnosi na ideju da je gomila računara povezana i da mogu međusobno slati poruke.
Reč distribuirano znači da ne postoji centralna stranka koja kontroliše, već da svi učesnici koordiniraju medjusobno kako bi mreža bila uspešna.
U sistemu bez centralne kontrole, bitno je znati da niko ne vara. Ideja dvostruke potrošnje odnosi se na mogućnost trošenja istog novca dva puta.
Fizički novac odlazi iz vaše ruke kad ga potrošite. Međutim, digitalne transakcije se mogu kopirati baš kao muzika ili filmovi.
Kada novac šaljete preko banke, oni se pobrinu da isti novac ne možete da prebacujete dva puta.
U sistemu bez centralne kontrole potreban nam je način da sprečimo ovu vrstu dvostruke potrošnje, koja je u suštini ista kao i falsifikovanje novca.
Satoshi opisuje da učesnici u Bitcoin mreži rade zajedno kako bi vremenski označili (doveli u red) transakcije kako bismo znali šta je bilo prvo.
Zbog toga možemo odbiti sve buduće pokušaje trošenja istog novca.
Satoshi se uhvatio u koštac sa nekoliko zanimljivih tehničkih problema kako bi rešio probleme privatnosti, uništavanja vrednosti i centralne kontrole u trenutnim monetarnim sistemima.
Na kraju je stvorio peer to peer mrežu kojoj se svako mogao pridružiti bez otkrivanja svog identiteta ili potrebe da veruje bilo kom drugom učesniku.
Kako se Bitcoin razvijao u poslednjoj deceniji?
Doprinosi izvornom kodu Bitcoina
Kada je Bitcoin pokrenut, samo nekolicina ljudi ga je koristila i pokrenula Bitcoin softver na svojim računarima za napajanje Bitcoin mreže.
Većina ljudi u to vreme mislila je da je to šala ili da će se otkriti ozbiljni nedostaci u dizajnu sistema koji će ga učiniti neizvodljivim.
Vremenom se mreži pridružilo sve više ljudi koji su pomoću svojih računara dodali sigurnost mreži.
Ljudi su počeli da menjaju Bitcoin-e za robu i usluge, dajući mu stvarnu vrednost. Pojavile su se menjačnice valuta koje su menjale Bitcoin-e za gotovo sve tradicionalne valute na svetu.
Deset godina nakon izuma, Bitcoin koriste milioni ljudi sa desetinama do stotinama hiljada čvorova koji pokreću besplatni Bitcoin softver, koji se razvija od strane stotina dobrovoljaca i kompanija širom sveta.
Bitcoin mreža je porasla kako bi obezbedila vrednost veću od stotine biliona dolara.
Računari koji učestvuju u zaštiti Bitcoin mreže poznati su kao rudari/majneri.
Oni rade u industrijskim operacijama širom sveta, ulažući milione dolara u specijalni rudarski hardver koji radi samo jedno: pobrinuti se da je Bitcoin najsigurnija mreža na planeti.
Rudari troše električnu energiju kako bi transakcije Bitcoin-a učinile sigurnim od modifikacija. Budući da se rudari međusobno takmiče za oskudan broj Bitcoin-a proizvedenih dnevno, oni uvek moraju da pronalaze najjeftinije izvore energije na planeti da bi ostali profitabilni.
Rudari rade na različitim mestima, od hidroelektrana u dalekim krajevima Kine do vetroparkova u Teksasu, do kanadskih naftnih polja koja proizvode gas koji bi u suprotnom bio odzračen ili spaljen u atmosferi.
Iako je Bitcoin popularna tema i o njemu se često raspravlja u medijima, procenjujemo da je samo nekoliko miliona ljudi na svetu počelo da redovno štedi Bitcoin.
Za mnoge ljude, posebno za one koji nikada nisu živeli pod represivnim režimima, ovaj izum novog oblika digitalnog novca izvan kontrole vlade može biti veoma izazovan za razumevanje i prihvatanje.
Zato sam ja ovde. Želim da vam pomognem da razumete Bitcoin i budete gospodar svoje budućnosti!
-
 @ 732c6a62:42003da2
2025-03-09 22:36:26
@ 732c6a62:42003da2
2025-03-09 22:36:26Não são recentes as táticas da esquerda de tentar reprimir intelectualmente seus opositores na base do deboche, da ironia, do desprezo e do boicote à credibilidade. Até Marx usava ironia para chamar os críticos de "burgueses iludidos". A diferença é que, no século XXI, trocaram o manifesto comunista por threads no Twitter e a dialética por memes de mau gosto.
A Falácia da Superioridade Moral
O debate sobre o "pobre de direita" no Brasil é contaminado por uma premissa tácita da esquerda: a ideia de que classes baixas só podem ter consciência política se aderirem a pautas progressistas. Quem ousa divergir é tratado como "traidor de classe", "manipulado", "ignorante", ou até vítimas de deboches como alguma pessoa com um qi em temperatura ambiente repetir diversas vezes "não é possível que ainda exista pobre de direita", "nunca vou entender pobre de direita", ou "pobre de direita é muito burro, rico eu até entendo", como se o autor dessas frases fosse o paladino dos mais oprimidos e pobres. Esse discurso, porém, não resiste a uma análise empírica, histórica ou sociológica.
Contexto Histórico: A Esquerda e o Mito do "Voto Consciente"
A noção de que o pobre deve votar na esquerda por "interesse de classe" é herança do marxismo ortodoxo, que via a política como mero reflexo da posição econômica. No entanto, a realidade é mais complexa:
- Dados do Latinobarómetro (2022): 41% dos brasileiros de baixa renda (até 2 salários mínimos) apoiam redução de impostos e maior liberdade econômica — pautas tradicionalmente associadas à direita.
- Pesquisa IPEC (2023): 58% dos pobres brasileiros priorizam "segurança pública" como principal demanda, acima de "distribuição de renda".
Esses números não são acidentais. Refletem uma mudança estrutural: o pobre moderno não é mais o "operário industrial" do século XX, mas um empreendedor informal, motorista de app, ou microempresário — figuras que valorizam autonomia e rejeitam paternalismo estatal. Eles dizem não entender o pobre de direita e que nunca vai entendê-los, mas o fato é que não entendem porque nunca conversaram com um sem fazer cara de psicólogo de posto de saúde. Sua "preocupação" é só uma máscara para esconder o desprezo por quem ousa pensar diferente do seu manual de "oprimido ideal".
Se ainda não entenderam:
Direita ≠ rico: Tem gente que trabalha 12h/dia e vota em liberal porque quer ser dono do próprio negócio, não pra pagar mais taxação pra você postar meme no Twitter.
Acham que são o Sherlock Holmes da pobreza: o palpite de que "o pobre é manipulado" é tão raso quanto sua compreensão de economia básica.
A Psicologia por Trás do Voto Conservador nas Periferias
A esquerda atribui o voto pobre em direita a "falta de educação" ou "manipulação midiática". Essa tese é não apenas elitista, mas cientificamente falsa:
Análise Psicológica Básica (para você que se acha o Paulo Freire):
- Síndrome do Branco Salvador: Acha que o pobre é uma criatura tão frágil que precisa de você pra pensar. Spoiler: ele não precisa.
- Viés da Superioridade Moral: "Se você é pobre e não concorda comigo, você é burro". Parabéns, recriou a escravidão intelectual.
- Efeito Dunning-Kruger: Não sabe o que é CLT, mas dá palpite sobre reforma trabalhista.- Estudo da Universidade de São Paulo (USP, 2021): Entre moradores de favelas, 63% associam políticas de segurança dura (como "bandido bom é bandido morto") à proteção de seus negócios e famílias. Para eles, a esquerda é "branda demais" com o crime.
- Pesquisa FGV (2020): 71% dos trabalhadores informais rejeitam aumentos de impostos, mesmo que para financiar programas sociais. Motivo: já sofrem com a burocracia estatal para legalizar seus negócios.
Esses dados revelam uma racionalidade prática: o pobre avalia políticas pelo impacto imediato em sua vida, não por abstrações ideológicas. Enquanto a esquerda fala em "reforma estrutural" e tenta importar discursos estrangeiros para debate, por exemplo, o tema irrelevante do pronome neutro, ele quer resolver problemas como:
- Violência (que afeta seu comércio);
- Impostos (que consomem até 40% do lucro de um camelô);
- Burocracia (que impede a legalização de sua barraca de pastel).
Religião, Valores e a Hipocrisia do "Ateísmo de Redes Sociais"
A esquerda subestima o papel da religião na formação política das classes baixas. No Brasil, 76% dos evangélicos são pobres (Datafolha, 2023), e suas igrejas promovem valores como:
- Família tradicional (contra pautas progressistas como ideologia de gênero em escolas);
- Auto-responsabilidade (ênfase em "trabalho duro" em vez de assistencialismo).Exemplo Concreto:
Nas favelas de São Paulo, pastores evangélicos são frequentemente eleitos a cargos locais com plataformas anticrime e pró-mercado. Para seus eleitores, a esquerda urbana (que defende descriminalização de drogas e críticas à polícia) representa uma ameaça ao seu estilo de vida.
A Esquerda e seu Desprezo pela Autonomia do Pobre
O cerne do debate é a incapacidade da esquerda de aceitar que o pobre possa ser autônomo. Algumas evidências:
O Caso dos Empreendedores Informais
- Segundo o IBGE (2023), 40% dos trabalhadores brasileiros estão na informalidade. Muitos veem o Estado como obstáculo, não aliado. Políticas de direita (como simplificação tributária) são mais atraentes para eles que o Bolsa Família.
A Ascensão do Conservadorismo Periférico
- Pessoas assim tem um pensamento simples. Sua mensagem: "Queremos empreender, não depender de político."
A Rejeição ao "Vitimismo"
- Pesquisa Atlas Intel (2022): 68% dos pobres brasileiros rejeitam o termo "vítima da sociedade". Preferem ser vistos como "lutadores".
A projeção freudiana "o pobre é burro porque eu sou inteligente"
O deboche esquerdista esconde um complexo de inferioridade disfarçado de superioridade moral. É a Síndrome do Salvador em sua forma mais patética:
- Passo 1: Assume-se que o pobre é um ser desprovido de agência.
- Passo 2: Qualquer desvio da narrativa é atribuído a "manipulação da elite".
- Passo 3: Quem critica o processo é chamado de "fascista".Exemplo Prático:
Quando uma empregada doméstica diz que prefere o livre mercado a programas sociais, a esquerda não pergunta "por quê?" — ela grita "lavagem cerebral!". A ironia? Essa mesma esquerda defende a autonomia feminina, exceto quando a mulher é pobre e pensa diferente.Dados Globais: O Fenômeno Não é Brasileiro
A ideia de que "pobre de direita" é uma anomalia é desmentida por evidências internacionais:
- Estados Unidos: 38% dos eleitores com renda abaixo de US$ 30k/ano votaram em Trump em 2020 (Pew Research). Motivos principais: conservadorismo social e rejeição a impostos. A esquerda: "vítimas da falsa consciência". Mais um detalhe: na última eleição de 2024, grande parte da classe "artística" milionária dos Estados Unidos, figuras conhecidas, promoveram em peso a Kamala Harris, do Partido Democrata. Percebe como a esquerda atual é a personificaçãoda burguesia e de só pensar na própria barriga?
- Argentina: Javier Milei, libertário radical, quando candidato, tinha forte apoio nas villas miseria (favelas). Seu lema — "O estado é um parasita" — ressoa entre quem sofria com inflação de 211% ao ano.
- Índia: O partido BJP (direita nacionalista) domina entre os pobres rurais, que associam a esquerda a elites urbanas desconectadas de suas necessidades.
A história que a esquerda tenta apagar: pobres de direita existem desde sempre
A esquerda age como se o "pobre de direita" fosse uma invenção recente do MBL, mas a realidade é que classes baixas conservadoras são regra, não exceção, na história mundial:
- Revolução Francesa (1789): Camponeses apoiaram a monarquia contra os jacobinos urbanos que queriam "libertá-los".
- Brasil Imperial: Escravos libertos que viraram pequenos proprietários rurais rejeitavam o abolicionismo radical — queriam integração, não utopia.Tradução:
Quando o pobre não segue o script, a esquerda inventa teorias conspiratórias.
A Hipocrisia da Esquerda Urbana e Universitária
Enquanto acusa o pobre de direita de "alienado", a esquerda brasileira é dominada por uma elite desconectada da realidade periférica:
- Perfil Socioeconômico: 82% dos filiados ao PSOL têm ensino superior completo (TSE, 2023). Apenas 6% moram em bairros periféricos.
- Prioridades Descoladas: Enquanto o pobre debate segurança e custo de vida, a esquerda pauta discussões como "linguagem não-binária em editais públicos" — tema irrelevante para quem luta contra o desemprego. Os grandes teóricos comunistas se reviram no túmulo quando veem o que a esquerda se tornou: não debatem os reais problemas do Brasil, e sim sobre suas próprias emoções.
"A esquerda brasileira trocou o operário pelo influencer progressista. O pobre virou um personagem de campanha, não um interlocutor real."
A diversidade de pensamento que a esquerda não suporta
A esquerda prega diversidade — desde que você seja diverso dentro de um checklist pré-aprovado. Pobre LGBTQ+? Herói. Pobre evangélico? Fascista. Pobre que abre MEI? "Peão do capitalismo". A realidade é que favelas e periferias são microcosmos de pluralidade ideológica, algo que assusta quem quer reduzir seres humanos a estereótipos.
Respostas aos Argumentos Esquerdistas (e Por que Falham)
"O pobre de direita é manipulado pela mídia!"
- Contradição: Se a mídia tradicional é dominada por elites (como alegam), por que grandes veículos são abertamente progressistas? A Record (evangélica) é exceção, não regra.
Contradição Central:
Como explicar que, segundo o Banco Mundial (2023), países com maior liberdade econômica (ex.: Chile, Polônia) reduziram a pobreza extrema em 60% nas últimas décadas, enquanto modelos estatizantes (ex.: Venezuela, Argentina com o governo peronista) afundaram na miséria? Simples: a esquerda prefere culpar o "neoliberalismo" a admitir que o pobre com o mínimo de consciência quer emprego, não esmola.Dado que Machuca:
- 71% das mulheres da periferia rejeitam o feminismo radical, associando-o a "prioridades distantes da realidade" (Instituto Locomotiva, 2023)."Ele vota contra os próprios interesses!"
- Falácia: Pressupõe que a esquerda define o que é o "interesse do pobre". Para um pai de família na Cidade de Deus, ter a boca de fogo fechada pode ser mais urgente que um aumento de 10% no Bolsa Família.
O pobre de direita não é uma anomalia. É o produto natural de um mundo complexo onde seres humanos têm aspirações, medos e valores diversos. Enquanto a esquerda insiste em tratá-lo como um projeto fracassado, ele está ocupado:
- Trabalhando para não depender do governo.
- Escolhendo religiões que dão sentido à sua vida.
- Rejeitando pautas identitárias que não resolvem o custo do gás de cozinha."É falta de educação política!"
- Ironia: Nos países nórdicos (modelo da esquerda), as classes baixas são as mais conservadoras. Educação não correlaciona com progressismo.
Por que o Debuste Precisa Acabar
A insistência em descredibilizar o pobre de direita revela um projeto de poder fracassado. A esquerda, ao substituir diálogo por deboche, perdeu a capacidade de representar quem mais precisaria dela. Enquanto isso, a direita — nem sempre por virtude, mas por pragmatismo — capturou o descontentamento de milhões com o status quo.
O pobre de direita existe porque ele não precisa da permissão do rico de esquerda para pensar. A incapacidade de entender isso só prova que a esquerda é a nova aristocracia.
Último Dado: Nas eleições de 2022, Tarcísio de Freitas (direita) venceu em 72% das favelas de São Paulo. O motivo? Seu discurso anti-burocracia e pró-microempreendedor.
A mensagem é clara: o pobre não é um projeto ideológico. É um agente político autônomo — e quem não entender isso continuará perdendo eleições.
A esquerda elitista não odeia o pobre de direita por ele ser "irracional". Odeia porque ele desafia o monopólio moral que ela construiu sobre a miséria alheia. Enquanto isso, o pobre segue sua vida, ignorando os berros de quem acha que sabem mais da sua vida que ele mesmo.
Pergunta Retórica (Para Incomodar):
Se a esquerda é tão sábia, por que não usa essa sabedoria para entender que pobre também cansa de ser tratado como cachorro que late no ritmo errado?
Fontes Citadas:
- Latinobarómetro (2022)
- IPEC (2023)
- USP (2021): "Segurança Pública e Percepções nas Favelas Cariocas"
- FGV (2020): "Informalidade e Tributação no Brasil"
- Datafolha (2023): "Perfil Religioso do Eleitorado Brasileiro"
- Atlas Intel (2022): "Autopercepção das Classes Baixas"
- Pew Research (2020): "Voting Patterns by Income in the U.S."
- TSE (2023): "Perfil Socioeconômico dos Filiados Partidários"
Leitura Recomendada para Esquerdistas:
- "Fome de Poder: Por que o Pobre Brasileiro Abandonou a Esquerda" (Fernando Schüller, 2023)
- "A Revolução dos Conservadores: Religião e Política nas Periferias" (Juliano Spyer, 2021)
- "Direita e Esquerda: Razões e Paixões" (Demétrio Magnoli, 2019) -
 @ 4857600b:30b502f4
2025-03-10 12:09:35
@ 4857600b:30b502f4
2025-03-10 12:09:35At this point, we should be arresting, not firing, any FBI employee who delays, destroys, or withholds information on the Epstein case. There is ZERO explanation I will accept for redacting anything for “national security” reasons. A lot of Trump supporters are losing patience with Pam Bondi. I will give her the benefit of the doubt for now since the corruption within the whole security/intelligence apparatus of our country runs deep. However, let’s not forget that probably Trump’s biggest mistakes in his first term involved picking weak and easily corruptible (or blackmailable) officials. It seemed every month a formerly-loyal person did a complete 180 degree turn and did everything they could to screw him over, regardless of the betrayal’s effect on the country or whatever principles that person claimed to have. I think he’s fixed his screening process, but since we’re talking about the FBI, we know they have the power to dig up any dirt or blackmail material available, or just make it up. In the Epstein case, it’s probably better to go after Bondi than give up a treasure trove of blackmail material against the long list of members on his client list.
-
 @ 6f6b50bb:a848e5a1
2024-12-15 15:09:52
@ 6f6b50bb:a848e5a1
2024-12-15 15:09:52Che cosa significherebbe trattare l'IA come uno strumento invece che come una persona?
Dall’avvio di ChatGPT, le esplorazioni in due direzioni hanno preso velocità.
La prima direzione riguarda le capacità tecniche. Quanto grande possiamo addestrare un modello? Quanto bene può rispondere alle domande del SAT? Con quanta efficienza possiamo distribuirlo?
La seconda direzione riguarda il design dell’interazione. Come comunichiamo con un modello? Come possiamo usarlo per un lavoro utile? Quale metafora usiamo per ragionare su di esso?
La prima direzione è ampiamente seguita e enormemente finanziata, e per una buona ragione: i progressi nelle capacità tecniche sono alla base di ogni possibile applicazione. Ma la seconda è altrettanto cruciale per il campo e ha enormi incognite. Siamo solo a pochi anni dall’inizio dell’era dei grandi modelli. Quali sono le probabilità che abbiamo già capito i modi migliori per usarli?
Propongo una nuova modalità di interazione, in cui i modelli svolgano il ruolo di applicazioni informatiche (ad esempio app per telefoni): fornendo un’interfaccia grafica, interpretando gli input degli utenti e aggiornando il loro stato. In questa modalità, invece di essere un “agente” che utilizza un computer per conto dell’essere umano, l’IA può fornire un ambiente informatico più ricco e potente che possiamo utilizzare.
Metafore per l’interazione
Al centro di un’interazione c’è una metafora che guida le aspettative di un utente su un sistema. I primi giorni dell’informatica hanno preso metafore come “scrivanie”, “macchine da scrivere”, “fogli di calcolo” e “lettere” e le hanno trasformate in equivalenti digitali, permettendo all’utente di ragionare sul loro comportamento. Puoi lasciare qualcosa sulla tua scrivania e tornare a prenderlo; hai bisogno di un indirizzo per inviare una lettera. Man mano che abbiamo sviluppato una conoscenza culturale di questi dispositivi, la necessità di queste particolari metafore è scomparsa, e con esse i design di interfaccia skeumorfici che le rafforzavano. Come un cestino o una matita, un computer è ora una metafora di se stesso.
La metafora dominante per i grandi modelli oggi è modello-come-persona. Questa è una metafora efficace perché le persone hanno capacità estese che conosciamo intuitivamente. Implica che possiamo avere una conversazione con un modello e porgli domande; che il modello possa collaborare con noi su un documento o un pezzo di codice; che possiamo assegnargli un compito da svolgere da solo e che tornerà quando sarà finito.
Tuttavia, trattare un modello come una persona limita profondamente il nostro modo di pensare all’interazione con esso. Le interazioni umane sono intrinsecamente lente e lineari, limitate dalla larghezza di banda e dalla natura a turni della comunicazione verbale. Come abbiamo tutti sperimentato, comunicare idee complesse in una conversazione è difficile e dispersivo. Quando vogliamo precisione, ci rivolgiamo invece a strumenti, utilizzando manipolazioni dirette e interfacce visive ad alta larghezza di banda per creare diagrammi, scrivere codice e progettare modelli CAD. Poiché concepiamo i modelli come persone, li utilizziamo attraverso conversazioni lente, anche se sono perfettamente in grado di accettare input diretti e rapidi e di produrre risultati visivi. Le metafore che utilizziamo limitano le esperienze che costruiamo, e la metafora modello-come-persona ci impedisce di esplorare il pieno potenziale dei grandi modelli.
Per molti casi d’uso, e specialmente per il lavoro produttivo, credo che il futuro risieda in un’altra metafora: modello-come-computer.
Usare un’IA come un computer
Sotto la metafora modello-come-computer, interagiremo con i grandi modelli seguendo le intuizioni che abbiamo sulle applicazioni informatiche (sia su desktop, tablet o telefono). Nota che ciò non significa che il modello sarà un’app tradizionale più di quanto il desktop di Windows fosse una scrivania letterale. “Applicazione informatica” sarà un modo per un modello di rappresentarsi a noi. Invece di agire come una persona, il modello agirà come un computer.
Agire come un computer significa produrre un’interfaccia grafica. Al posto del flusso lineare di testo in stile telescrivente fornito da ChatGPT, un sistema modello-come-computer genererà qualcosa che somiglia all’interfaccia di un’applicazione moderna: pulsanti, cursori, schede, immagini, grafici e tutto il resto. Questo affronta limitazioni chiave dell’interfaccia di chat standard modello-come-persona:
-
Scoperta. Un buon strumento suggerisce i suoi usi. Quando l’unica interfaccia è una casella di testo vuota, spetta all’utente capire cosa fare e comprendere i limiti del sistema. La barra laterale Modifica in Lightroom è un ottimo modo per imparare l’editing fotografico perché non si limita a dirti cosa può fare questa applicazione con una foto, ma cosa potresti voler fare. Allo stesso modo, un’interfaccia modello-come-computer per DALL-E potrebbe mostrare nuove possibilità per le tue generazioni di immagini.
-
Efficienza. La manipolazione diretta è più rapida che scrivere una richiesta a parole. Per continuare l’esempio di Lightroom, sarebbe impensabile modificare una foto dicendo a una persona quali cursori spostare e di quanto. Ci vorrebbe un giorno intero per chiedere un’esposizione leggermente più bassa e una vibranza leggermente più alta, solo per vedere come apparirebbe. Nella metafora modello-come-computer, il modello può creare strumenti che ti permettono di comunicare ciò che vuoi più efficientemente e quindi di fare le cose più rapidamente.
A differenza di un’app tradizionale, questa interfaccia grafica è generata dal modello su richiesta. Questo significa che ogni parte dell’interfaccia che vedi è rilevante per ciò che stai facendo in quel momento, inclusi i contenuti specifici del tuo lavoro. Significa anche che, se desideri un’interfaccia più ampia o diversa, puoi semplicemente richiederla. Potresti chiedere a DALL-E di produrre alcuni preset modificabili per le sue impostazioni ispirati da famosi artisti di schizzi. Quando clicchi sul preset Leonardo da Vinci, imposta i cursori per disegni prospettici altamente dettagliati in inchiostro nero. Se clicchi su Charles Schulz, seleziona fumetti tecnicolor 2D a basso dettaglio.
Una bicicletta della mente proteiforme
La metafora modello-come-persona ha una curiosa tendenza a creare distanza tra l’utente e il modello, rispecchiando il divario di comunicazione tra due persone che può essere ridotto ma mai completamente colmato. A causa della difficoltà e del costo di comunicare a parole, le persone tendono a suddividere i compiti tra loro in blocchi grandi e il più indipendenti possibile. Le interfacce modello-come-persona seguono questo schema: non vale la pena dire a un modello di aggiungere un return statement alla tua funzione quando è più veloce scriverlo da solo. Con il sovraccarico della comunicazione, i sistemi modello-come-persona sono più utili quando possono fare un intero blocco di lavoro da soli. Fanno le cose per te.
Questo contrasta con il modo in cui interagiamo con i computer o altri strumenti. Gli strumenti producono feedback visivi in tempo reale e sono controllati attraverso manipolazioni dirette. Hanno un overhead comunicativo così basso che non è necessario specificare un blocco di lavoro indipendente. Ha più senso mantenere l’umano nel loop e dirigere lo strumento momento per momento. Come stivali delle sette leghe, gli strumenti ti permettono di andare più lontano a ogni passo, ma sei ancora tu a fare il lavoro. Ti permettono di fare le cose più velocemente.
Considera il compito di costruire un sito web usando un grande modello. Con le interfacce di oggi, potresti trattare il modello come un appaltatore o un collaboratore. Cercheresti di scrivere a parole il più possibile su come vuoi che il sito appaia, cosa vuoi che dica e quali funzionalità vuoi che abbia. Il modello genererebbe una prima bozza, tu la eseguirai e poi fornirai un feedback. “Fai il logo un po’ più grande”, diresti, e “centra quella prima immagine principale”, e “deve esserci un pulsante di login nell’intestazione”. Per ottenere esattamente ciò che vuoi, invierai una lista molto lunga di richieste sempre più minuziose.
Un’interazione alternativa modello-come-computer sarebbe diversa: invece di costruire il sito web, il modello genererebbe un’interfaccia per te per costruirlo, dove ogni input dell’utente a quell’interfaccia interroga il grande modello sotto il cofano. Forse quando descrivi le tue necessità creerebbe un’interfaccia con una barra laterale e una finestra di anteprima. All’inizio la barra laterale contiene solo alcuni schizzi di layout che puoi scegliere come punto di partenza. Puoi cliccare su ciascuno di essi, e il modello scrive l’HTML per una pagina web usando quel layout e lo visualizza nella finestra di anteprima. Ora che hai una pagina su cui lavorare, la barra laterale guadagna opzioni aggiuntive che influenzano la pagina globalmente, come accoppiamenti di font e schemi di colore. L’anteprima funge da editor WYSIWYG, permettendoti di afferrare elementi e spostarli, modificarne i contenuti, ecc. A supportare tutto ciò è il modello, che vede queste azioni dell’utente e riscrive la pagina per corrispondere ai cambiamenti effettuati. Poiché il modello può generare un’interfaccia per aiutare te e lui a comunicare più efficientemente, puoi esercitare più controllo sul prodotto finale in meno tempo.
La metafora modello-come-computer ci incoraggia a pensare al modello come a uno strumento con cui interagire in tempo reale piuttosto che a un collaboratore a cui assegnare compiti. Invece di sostituire un tirocinante o un tutor, può essere una sorta di bicicletta proteiforme per la mente, una che è sempre costruita su misura esattamente per te e il terreno che intendi attraversare.
Un nuovo paradigma per l’informatica?
I modelli che possono generare interfacce su richiesta sono una frontiera completamente nuova nell’informatica. Potrebbero essere un paradigma del tutto nuovo, con il modo in cui cortocircuitano il modello di applicazione esistente. Dare agli utenti finali il potere di creare e modificare app al volo cambia fondamentalmente il modo in cui interagiamo con i computer. Al posto di una singola applicazione statica costruita da uno sviluppatore, un modello genererà un’applicazione su misura per l’utente e le sue esigenze immediate. Al posto della logica aziendale implementata nel codice, il modello interpreterà gli input dell’utente e aggiornerà l’interfaccia utente. È persino possibile che questo tipo di interfaccia generativa sostituisca completamente il sistema operativo, generando e gestendo interfacce e finestre al volo secondo necessità.
All’inizio, l’interfaccia generativa sarà un giocattolo, utile solo per l’esplorazione creativa e poche altre applicazioni di nicchia. Dopotutto, nessuno vorrebbe un’app di posta elettronica che occasionalmente invia email al tuo ex e mente sulla tua casella di posta. Ma gradualmente i modelli miglioreranno. Anche mentre si spingeranno ulteriormente nello spazio di esperienze completamente nuove, diventeranno lentamente abbastanza affidabili da essere utilizzati per un lavoro reale.
Piccoli pezzi di questo futuro esistono già. Anni fa Jonas Degrave ha dimostrato che ChatGPT poteva fare una buona simulazione di una riga di comando Linux. Allo stesso modo, websim.ai utilizza un LLM per generare siti web su richiesta mentre li navighi. Oasis, GameNGen e DIAMOND addestrano modelli video condizionati sull’azione su singoli videogiochi, permettendoti di giocare ad esempio a Doom dentro un grande modello. E Genie 2 genera videogiochi giocabili da prompt testuali. L’interfaccia generativa potrebbe ancora sembrare un’idea folle, ma non è così folle.
Ci sono enormi domande aperte su come apparirà tutto questo. Dove sarà inizialmente utile l’interfaccia generativa? Come condivideremo e distribuiremo le esperienze che creiamo collaborando con il modello, se esistono solo come contesto di un grande modello? Vorremmo davvero farlo? Quali nuovi tipi di esperienze saranno possibili? Come funzionerà tutto questo in pratica? I modelli genereranno interfacce come codice o produrranno direttamente pixel grezzi?
Non conosco ancora queste risposte. Dovremo sperimentare e scoprirlo!Che cosa significherebbe trattare l'IA come uno strumento invece che come una persona?
Dall’avvio di ChatGPT, le esplorazioni in due direzioni hanno preso velocità.
La prima direzione riguarda le capacità tecniche. Quanto grande possiamo addestrare un modello? Quanto bene può rispondere alle domande del SAT? Con quanta efficienza possiamo distribuirlo?
La seconda direzione riguarda il design dell’interazione. Come comunichiamo con un modello? Come possiamo usarlo per un lavoro utile? Quale metafora usiamo per ragionare su di esso?
La prima direzione è ampiamente seguita e enormemente finanziata, e per una buona ragione: i progressi nelle capacità tecniche sono alla base di ogni possibile applicazione. Ma la seconda è altrettanto cruciale per il campo e ha enormi incognite. Siamo solo a pochi anni dall’inizio dell’era dei grandi modelli. Quali sono le probabilità che abbiamo già capito i modi migliori per usarli?
Propongo una nuova modalità di interazione, in cui i modelli svolgano il ruolo di applicazioni informatiche (ad esempio app per telefoni): fornendo un’interfaccia grafica, interpretando gli input degli utenti e aggiornando il loro stato. In questa modalità, invece di essere un “agente” che utilizza un computer per conto dell’essere umano, l’IA può fornire un ambiente informatico più ricco e potente che possiamo utilizzare.
Metafore per l’interazione
Al centro di un’interazione c’è una metafora che guida le aspettative di un utente su un sistema. I primi giorni dell’informatica hanno preso metafore come “scrivanie”, “macchine da scrivere”, “fogli di calcolo” e “lettere” e le hanno trasformate in equivalenti digitali, permettendo all’utente di ragionare sul loro comportamento. Puoi lasciare qualcosa sulla tua scrivania e tornare a prenderlo; hai bisogno di un indirizzo per inviare una lettera. Man mano che abbiamo sviluppato una conoscenza culturale di questi dispositivi, la necessità di queste particolari metafore è scomparsa, e con esse i design di interfaccia skeumorfici che le rafforzavano. Come un cestino o una matita, un computer è ora una metafora di se stesso.
La metafora dominante per i grandi modelli oggi è modello-come-persona. Questa è una metafora efficace perché le persone hanno capacità estese che conosciamo intuitivamente. Implica che possiamo avere una conversazione con un modello e porgli domande; che il modello possa collaborare con noi su un documento o un pezzo di codice; che possiamo assegnargli un compito da svolgere da solo e che tornerà quando sarà finito.
Tuttavia, trattare un modello come una persona limita profondamente il nostro modo di pensare all’interazione con esso. Le interazioni umane sono intrinsecamente lente e lineari, limitate dalla larghezza di banda e dalla natura a turni della comunicazione verbale. Come abbiamo tutti sperimentato, comunicare idee complesse in una conversazione è difficile e dispersivo. Quando vogliamo precisione, ci rivolgiamo invece a strumenti, utilizzando manipolazioni dirette e interfacce visive ad alta larghezza di banda per creare diagrammi, scrivere codice e progettare modelli CAD. Poiché concepiamo i modelli come persone, li utilizziamo attraverso conversazioni lente, anche se sono perfettamente in grado di accettare input diretti e rapidi e di produrre risultati visivi. Le metafore che utilizziamo limitano le esperienze che costruiamo, e la metafora modello-come-persona ci impedisce di esplorare il pieno potenziale dei grandi modelli.
Per molti casi d’uso, e specialmente per il lavoro produttivo, credo che il futuro risieda in un’altra metafora: modello-come-computer.
Usare un’IA come un computer
Sotto la metafora modello-come-computer, interagiremo con i grandi modelli seguendo le intuizioni che abbiamo sulle applicazioni informatiche (sia su desktop, tablet o telefono). Nota che ciò non significa che il modello sarà un’app tradizionale più di quanto il desktop di Windows fosse una scrivania letterale. “Applicazione informatica” sarà un modo per un modello di rappresentarsi a noi. Invece di agire come una persona, il modello agirà come un computer.
Agire come un computer significa produrre un’interfaccia grafica. Al posto del flusso lineare di testo in stile telescrivente fornito da ChatGPT, un sistema modello-come-computer genererà qualcosa che somiglia all’interfaccia di un’applicazione moderna: pulsanti, cursori, schede, immagini, grafici e tutto il resto. Questo affronta limitazioni chiave dell’interfaccia di chat standard modello-come-persona:
Scoperta. Un buon strumento suggerisce i suoi usi. Quando l’unica interfaccia è una casella di testo vuota, spetta all’utente capire cosa fare e comprendere i limiti del sistema. La barra laterale Modifica in Lightroom è un ottimo modo per imparare l’editing fotografico perché non si limita a dirti cosa può fare questa applicazione con una foto, ma cosa potresti voler fare. Allo stesso modo, un’interfaccia modello-come-computer per DALL-E potrebbe mostrare nuove possibilità per le tue generazioni di immagini.
Efficienza. La manipolazione diretta è più rapida che scrivere una richiesta a parole. Per continuare l’esempio di Lightroom, sarebbe impensabile modificare una foto dicendo a una persona quali cursori spostare e di quanto. Ci vorrebbe un giorno intero per chiedere un’esposizione leggermente più bassa e una vibranza leggermente più alta, solo per vedere come apparirebbe. Nella metafora modello-come-computer, il modello può creare strumenti che ti permettono di comunicare ciò che vuoi più efficientemente e quindi di fare le cose più rapidamente.
A differenza di un’app tradizionale, questa interfaccia grafica è generata dal modello su richiesta. Questo significa che ogni parte dell’interfaccia che vedi è rilevante per ciò che stai facendo in quel momento, inclusi i contenuti specifici del tuo lavoro. Significa anche che, se desideri un’interfaccia più ampia o diversa, puoi semplicemente richiederla. Potresti chiedere a DALL-E di produrre alcuni preset modificabili per le sue impostazioni ispirati da famosi artisti di schizzi. Quando clicchi sul preset Leonardo da Vinci, imposta i cursori per disegni prospettici altamente dettagliati in inchiostro nero. Se clicchi su Charles Schulz, seleziona fumetti tecnicolor 2D a basso dettaglio.
Una bicicletta della mente proteiforme
La metafora modello-come-persona ha una curiosa tendenza a creare distanza tra l’utente e il modello, rispecchiando il divario di comunicazione tra due persone che può essere ridotto ma mai completamente colmato. A causa della difficoltà e del costo di comunicare a parole, le persone tendono a suddividere i compiti tra loro in blocchi grandi e il più indipendenti possibile. Le interfacce modello-come-persona seguono questo schema: non vale la pena dire a un modello di aggiungere un return statement alla tua funzione quando è più veloce scriverlo da solo. Con il sovraccarico della comunicazione, i sistemi modello-come-persona sono più utili quando possono fare un intero blocco di lavoro da soli. Fanno le cose per te.
Questo contrasta con il modo in cui interagiamo con i computer o altri strumenti. Gli strumenti producono feedback visivi in tempo reale e sono controllati attraverso manipolazioni dirette. Hanno un overhead comunicativo così basso che non è necessario specificare un blocco di lavoro indipendente. Ha più senso mantenere l’umano nel loop e dirigere lo strumento momento per momento. Come stivali delle sette leghe, gli strumenti ti permettono di andare più lontano a ogni passo, ma sei ancora tu a fare il lavoro. Ti permettono di fare le cose più velocemente.
Considera il compito di costruire un sito web usando un grande modello. Con le interfacce di oggi, potresti trattare il modello come un appaltatore o un collaboratore. Cercheresti di scrivere a parole il più possibile su come vuoi che il sito appaia, cosa vuoi che dica e quali funzionalità vuoi che abbia. Il modello genererebbe una prima bozza, tu la eseguirai e poi fornirai un feedback. “Fai il logo un po’ più grande”, diresti, e “centra quella prima immagine principale”, e “deve esserci un pulsante di login nell’intestazione”. Per ottenere esattamente ciò che vuoi, invierai una lista molto lunga di richieste sempre più minuziose.
Un’interazione alternativa modello-come-computer sarebbe diversa: invece di costruire il sito web, il modello genererebbe un’interfaccia per te per costruirlo, dove ogni input dell’utente a quell’interfaccia interroga il grande modello sotto il cofano. Forse quando descrivi le tue necessità creerebbe un’interfaccia con una barra laterale e una finestra di anteprima. All’inizio la barra laterale contiene solo alcuni schizzi di layout che puoi scegliere come punto di partenza. Puoi cliccare su ciascuno di essi, e il modello scrive l’HTML per una pagina web usando quel layout e lo visualizza nella finestra di anteprima. Ora che hai una pagina su cui lavorare, la barra laterale guadagna opzioni aggiuntive che influenzano la pagina globalmente, come accoppiamenti di font e schemi di colore. L’anteprima funge da editor WYSIWYG, permettendoti di afferrare elementi e spostarli, modificarne i contenuti, ecc. A supportare tutto ciò è il modello, che vede queste azioni dell’utente e riscrive la pagina per corrispondere ai cambiamenti effettuati. Poiché il modello può generare un’interfaccia per aiutare te e lui a comunicare più efficientemente, puoi esercitare più controllo sul prodotto finale in meno tempo.
La metafora modello-come-computer ci incoraggia a pensare al modello come a uno strumento con cui interagire in tempo reale piuttosto che a un collaboratore a cui assegnare compiti. Invece di sostituire un tirocinante o un tutor, può essere una sorta di bicicletta proteiforme per la mente, una che è sempre costruita su misura esattamente per te e il terreno che intendi attraversare.
Un nuovo paradigma per l’informatica?
I modelli che possono generare interfacce su richiesta sono una frontiera completamente nuova nell’informatica. Potrebbero essere un paradigma del tutto nuovo, con il modo in cui cortocircuitano il modello di applicazione esistente. Dare agli utenti finali il potere di creare e modificare app al volo cambia fondamentalmente il modo in cui interagiamo con i computer. Al posto di una singola applicazione statica costruita da uno sviluppatore, un modello genererà un’applicazione su misura per l’utente e le sue esigenze immediate. Al posto della logica aziendale implementata nel codice, il modello interpreterà gli input dell’utente e aggiornerà l’interfaccia utente. È persino possibile che questo tipo di interfaccia generativa sostituisca completamente il sistema operativo, generando e gestendo interfacce e finestre al volo secondo necessità.
All’inizio, l’interfaccia generativa sarà un giocattolo, utile solo per l’esplorazione creativa e poche altre applicazioni di nicchia. Dopotutto, nessuno vorrebbe un’app di posta elettronica che occasionalmente invia email al tuo ex e mente sulla tua casella di posta. Ma gradualmente i modelli miglioreranno. Anche mentre si spingeranno ulteriormente nello spazio di esperienze completamente nuove, diventeranno lentamente abbastanza affidabili da essere utilizzati per un lavoro reale.
Piccoli pezzi di questo futuro esistono già. Anni fa Jonas Degrave ha dimostrato che ChatGPT poteva fare una buona simulazione di una riga di comando Linux. Allo stesso modo, websim.ai utilizza un LLM per generare siti web su richiesta mentre li navighi. Oasis, GameNGen e DIAMOND addestrano modelli video condizionati sull’azione su singoli videogiochi, permettendoti di giocare ad esempio a Doom dentro un grande modello. E Genie 2 genera videogiochi giocabili da prompt testuali. L’interfaccia generativa potrebbe ancora sembrare un’idea folle, ma non è così folle.
Ci sono enormi domande aperte su come apparirà tutto questo. Dove sarà inizialmente utile l’interfaccia generativa? Come condivideremo e distribuiremo le esperienze che creiamo collaborando con il modello, se esistono solo come contesto di un grande modello? Vorremmo davvero farlo? Quali nuovi tipi di esperienze saranno possibili? Come funzionerà tutto questo in pratica? I modelli genereranno interfacce come codice o produrranno direttamente pixel grezzi?
Non conosco ancora queste risposte. Dovremo sperimentare e scoprirlo!
Tradotto da:\ https://willwhitney.com/computing-inside-ai.htmlhttps://willwhitney.com/computing-inside-ai.html
-
-
 @ e6817453:b0ac3c39
2024-12-07 15:06:43
@ e6817453:b0ac3c39
2024-12-07 15:06:43I started a long series of articles about how to model different types of knowledge graphs in the relational model, which makes on-device memory models for AI agents possible.
We model-directed graphs
Also, graphs of entities
We even model hypergraphs
Last time, we discussed why classical triple and simple knowledge graphs are insufficient for AI agents and complex memory, especially in the domain of time-aware or multi-model knowledge.
So why do we need metagraphs, and what kind of challenge could they help us to solve?
- complex and nested event and temporal context and temporal relations as edges
- multi-mode and multilingual knowledge
- human-like memory for AI agents that has multiple contexts and relations between knowledge in neuron-like networks
MetaGraphs
A meta graph is a concept that extends the idea of a graph by allowing edges to become graphs. Meta Edges connect a set of nodes, which could also be subgraphs. So, at some level, node and edge are pretty similar in properties but act in different roles in a different context.
Also, in some cases, edges could be referenced as nodes.
This approach enables the representation of more complex relationships and hierarchies than a traditional graph structure allows. Let’s break down each term to understand better metagraphs and how they differ from hypergraphs and graphs.Graph Basics
- A standard graph has a set of nodes (or vertices) and edges (connections between nodes).
- Edges are generally simple and typically represent a binary relationship between two nodes.
- For instance, an edge in a social network graph might indicate a “friend” relationship between two people (nodes).
Hypergraph
- A hypergraph extends the concept of an edge by allowing it to connect any number of nodes, not just two.
- Each connection, called a hyperedge, can link multiple nodes.
- This feature allows hypergraphs to model more complex relationships involving multiple entities simultaneously. For example, a hyperedge in a hypergraph could represent a project team, connecting all team members in a single relation.
- Despite its flexibility, a hypergraph doesn’t capture hierarchical or nested structures; it only generalizes the number of connections in an edge.
Metagraph
- A metagraph allows the edges to be graphs themselves. This means each edge can contain its own nodes and edges, creating nested, hierarchical structures.
- In a meta graph, an edge could represent a relationship defined by a graph. For instance, a meta graph could represent a network of organizations where each organization’s structure (departments and connections) is represented by its own internal graph and treated as an edge in the larger meta graph.
- This recursive structure allows metagraphs to model complex data with multiple layers of abstraction. They can capture multi-node relationships (as in hypergraphs) and detailed, structured information about each relationship.
Named Graphs and Graph of Graphs
As you can notice, the structure of a metagraph is quite complex and could be complex to model in relational and classical RDF setups. It could create a challenge of luck of tools and software solutions for your problem.
If you need to model nested graphs, you could use a much simpler model of Named graphs, which could take you quite far.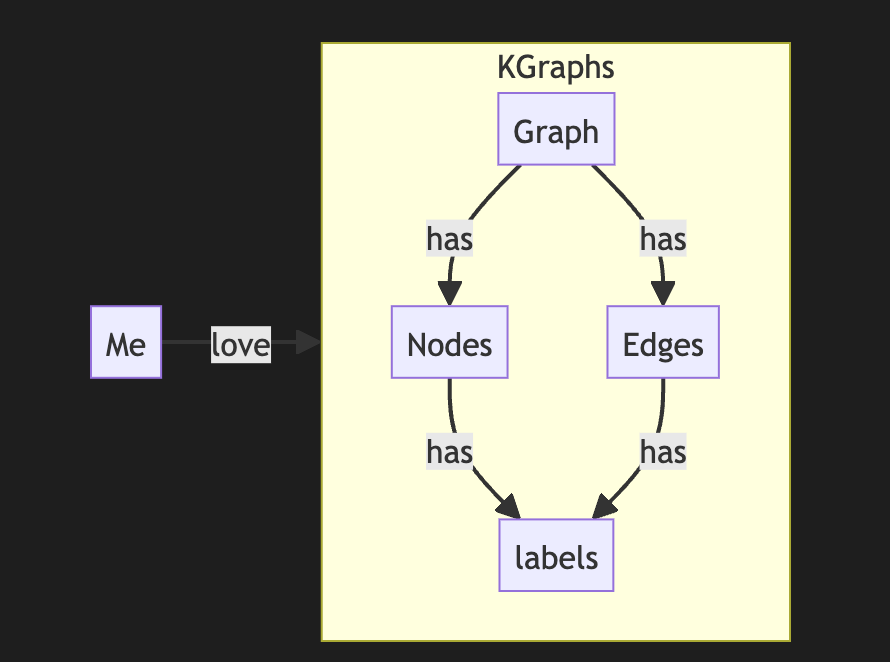
The concept of the named graph came from the RDF community, which needed to group some sets of triples. In this way, you form subgraphs inside an existing graph. You could refer to the subgraph as a regular node. This setup simplifies complex graphs, introduces hierarchies, and even adds features and properties of hypergraphs while keeping a directed nature.
It looks complex, but it is not so hard to model it with a slight modification of a directed graph.
So, the node could host graphs inside. Let's reflect this fact with a location for a node. If a node belongs to a main graph, we could set the location to null or introduce a main node . it is up to you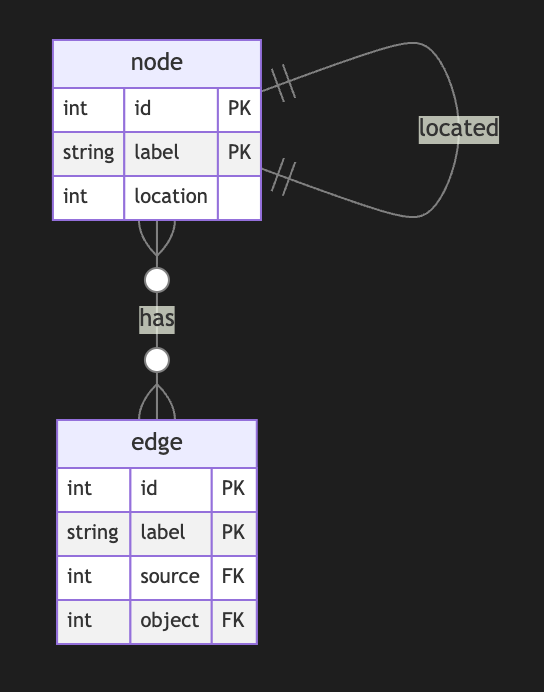
Nodes could have edges to nodes in different subgraphs. This structure allows any kind of nesting graphs. Edges stay location-free
Meta Graphs in Relational Model
Let’s try to make several attempts to model different meta-graphs with some constraints.
Directed Metagraph where edges are not used as nodes and could not contain subgraphs
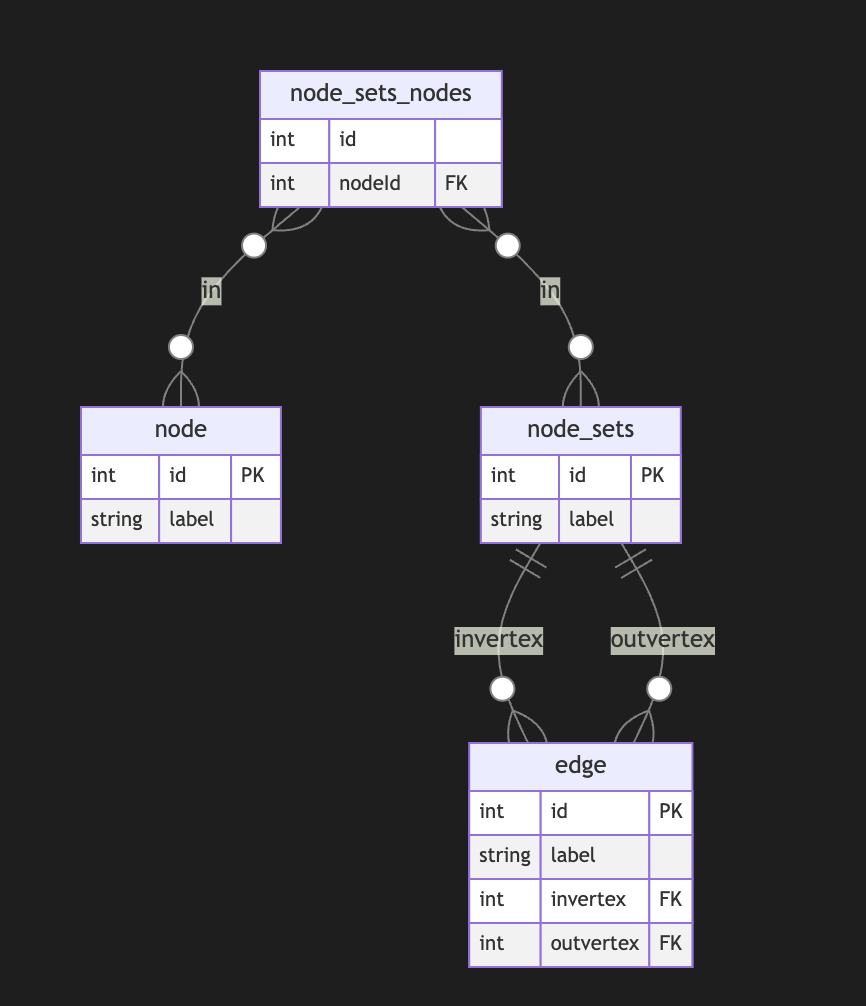
In this case, the edge always points to two sets of nodes. This introduces an overhead of creating a node set for a single node. In this model, we can model empty node sets that could require application-level constraints to prevent such cases.
Directed Metagraph where edges are not used as nodes and could contain subgraphs
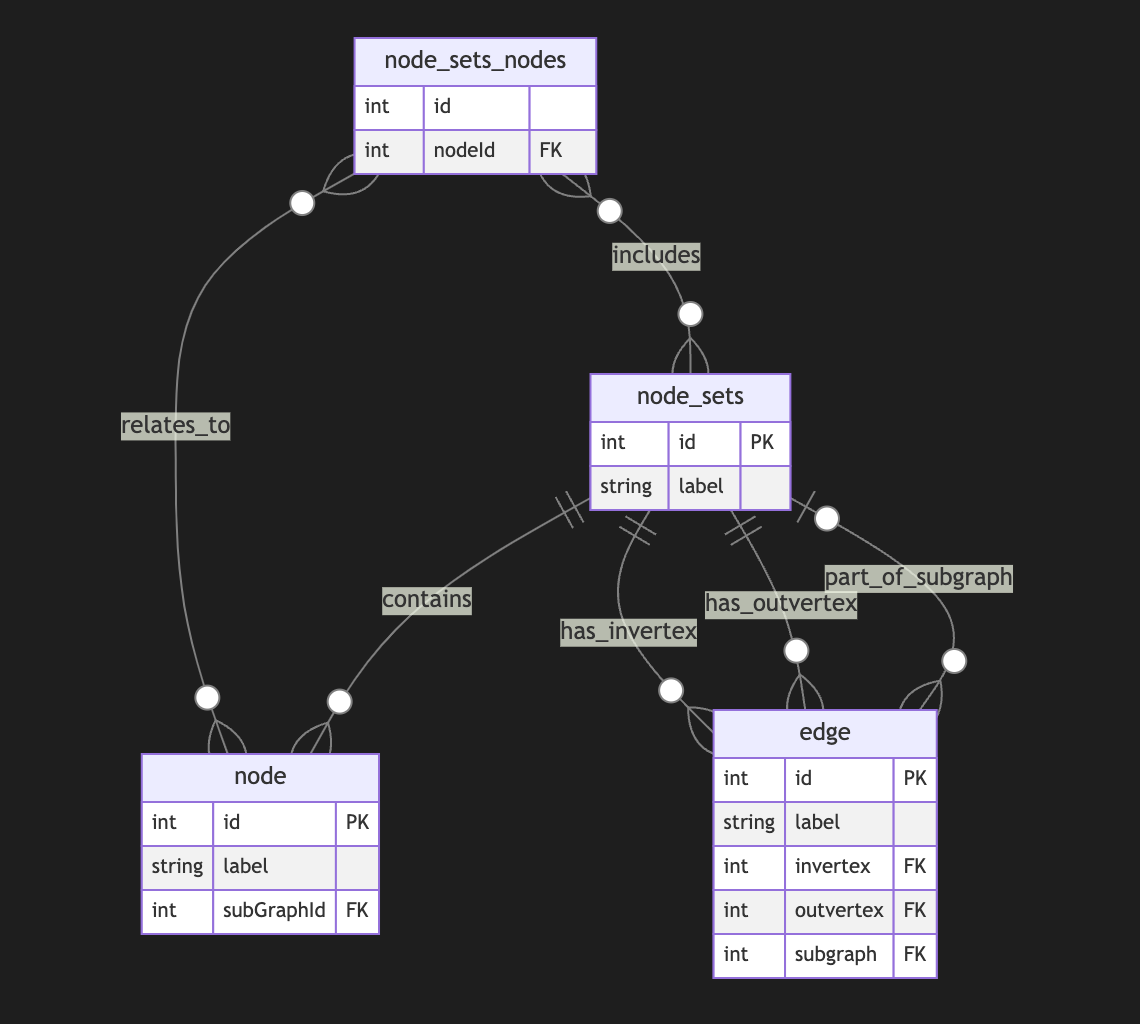
Adding a node set that could model a subgraph located in an edge is easy but could be separate from in-vertex or out-vert.
I also do not see a direct need to include subgraphs to a node, as we could just use a node set interchangeably, but it still could be a case.Directed Metagraph where edges are used as nodes and could contain subgraphs
As you can notice, we operate all the time with node sets. We could simply allow the extension node set to elements set that include node and edge IDs, but in this case, we need to use uuid or any other strategy to differentiate node IDs from edge IDs. In this case, we have a collision of ephemeral edges or ephemeral nodes when we want to change the role and purpose of the node as an edge or vice versa.
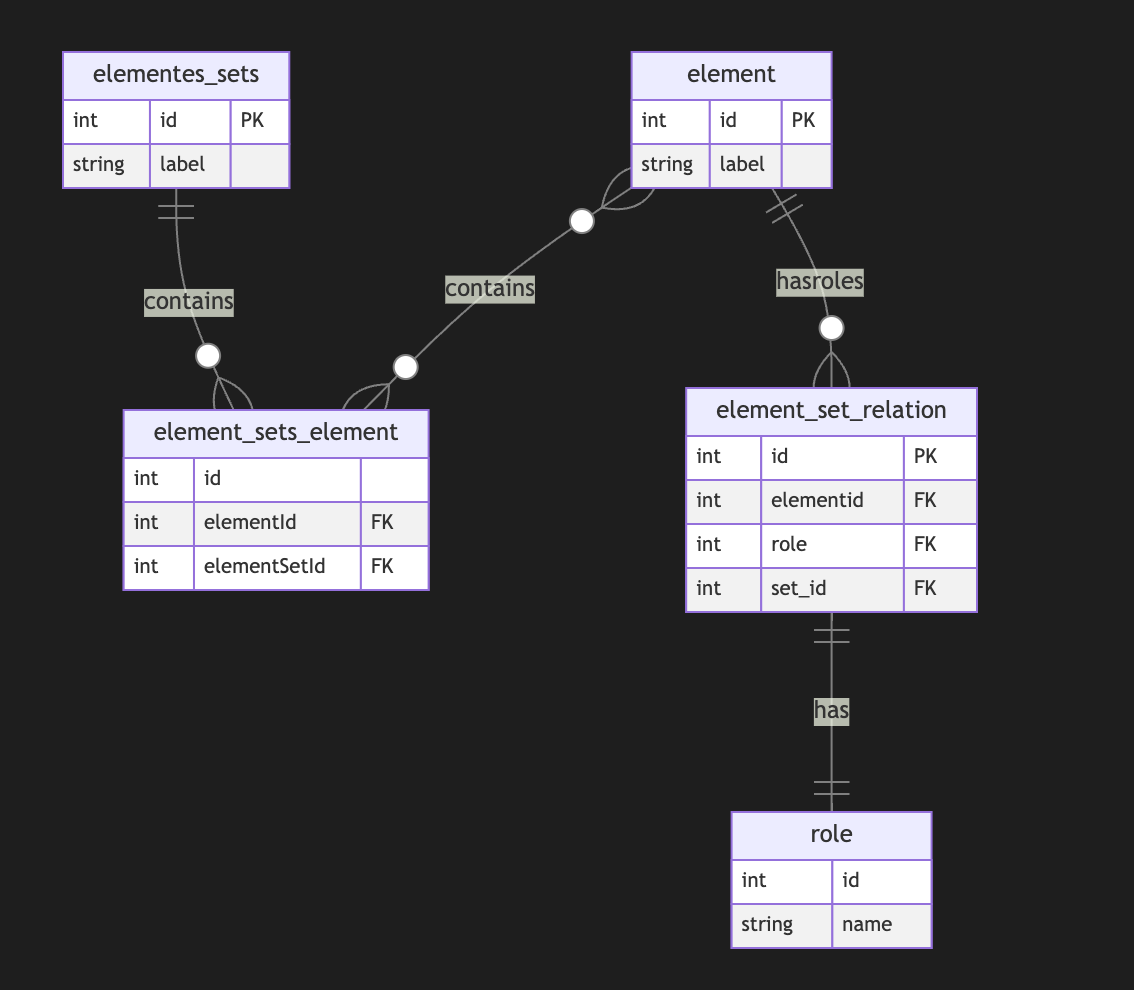
A full-scale metagraph model is way too complex for a relational database.
So we need a better model.Now, we have more flexibility but loose structural constraints. We cannot show that the element should have one vertex, one vertex, or both. This type of constraint has been moved to the application level. Also, the crucial question is about query and retrieval needs.
Any meta-graph model should be more focused on domain and needs and should be used in raw form. We did it for a pure theoretical purpose. -
 @ cff1720e:15c7e2b2
2025-05-24 20:17:45
@ cff1720e:15c7e2b2
2025-05-24 20:17:45Ich liebe Pareto. Für das was es ist, viel mehr aber für das was es derzeit wird - der Marktplatz der Ideen. Er entsteht durch gemeinsames Engagement von Entwicklern, Autoren und aktiven Lesern. Es ist ein lebendiges Medium, das jeden Tag wächst, quantitativ wie qualitativ, durch offene Interaktion, was es in dieser Form einzigartig macht.\ \ Mein Text ist inspiriert durch den Artikel von Alexa Rodrian vom 22. Mai über den Auftritt von Wolf Biermann bei der Verleihung des Deutschen Filmpreises. Alexa ist keine Publizistin, genau wie zahlreiche unserer Autoren, aber sie hat einen bemerkenswerten Beitrag verfasst. Ich habe ihn spontan geliked, kommentiert und mit einer Spende honoriert. In den vergangenen Tagen habe ich viel darüber reflektiert, und Pareto ermöglicht es mir, und jedem anderen, diese Überlegungen zur “Causa Biermann” hier darzulegen.

MSN kommentierte die anstößige Rede wie folgt: mit einem verfälschten Golda-Meir-Zitat lenkte Biermann das Thema auf das Sterben in Gaza, für das er die Palästinenser selbst verantwortlich machte. „Dass ihr unsere Söhne ermordet habt, werden wir Euch eines Tages verzeihen“, habe Meir zu den Palästinensern gesagt, „aber wir werden euch niemals verzeihen können, dass ihr unsere Söhne gezwungen habt, selber Mörder zu werden.“ Alexa Rodrian, in einer Mischung aus Enttäuschung und Empörung, eröffnete ihren Artikel wie folgt:

„Triff niemals deine Idole“ heißt ein gängiger Ratschlag. In gewendeten Zeiten stehen zu dem die Werte auf dem Kopf – und manche Künstler mit ihnen. Die Worte, die aus manch ihrer Mündern kommen, wirken, als hätte eine fremde Hand sie auf deren Zunge gelegt. Die fremde Hand ist bei Biermann eher unwahrscheinlich, denn sein Hang zu Provokationen und Verletzungen haben Tradition, man erinnere sich an den legendären Auftritt bei einer Feierstunde im Bundestag 2014 in der er die Mitglieder der Linksfraktion als “elenden Rest“ und ”Drachenbrut” bezeichnete. Oder seine Beschimpfungen der (ostdeutschen) Wähler von AfD und BSW im August 2024 in einem Zeit-Interview: „Die, die zu feige waren in der Diktatur, rebellieren jetzt ohne Risiko gegen die Demokratie. Den Bequemlichkeiten der Diktatur jammern sie nach, und die Mühen der Demokratie sind ihnen fremd.“
Im Februar 2025 wurde Wolf Biermann für sein Lebenswerk mit einem Musikpreis der GEMA ausgezeichnet. Was aber ist sein Lebenswerk, sein mutiges Engagement in der Opposition der DDR bis 1976 oder seine verfehlten Rüpeleien in der Gegenwart? Ein solcher Preis ist fragwürdig, denn kein Lebenswerk ist konsistent, und die Bewertung abhängig von subjektiven Maßstäben. Meist wählen wir unsere Idole nach unseren Idealen, aber die können sich verändern, ebenso wie das Idol. Beethoven widmete seine 3. Sinfonie (Eroica) Napoleon, zog die Widmung aber zurück als dieser sich 1804 zum Kaiser krönen ließ. “Ist der auch nichts anderes, wie ein gewöhnlicher Mensch?” soll er wütend ausgerufen haben. Richtig! Was hatte Beethoven erwartet, einen Gott? “Hosianna” und “kreuzigt ihn” sind Affekte die durch unsere Projektionen verursacht und den Realitäten nie gerecht werden.

Den Preis für sein Lebenswerk kann Wolf Biermann behalten. Er hat Millionen von Menschen in der DDR Mut gemacht. Er hat zahlreiche großartige Gedichte und Lieder verfasst, das behalte ich gerne in Erinnerung. Nun hat er sich selbst vom Sockel gestürzt und durch seinen Empathiemangel das Image beschädigt. Das hätte er vermeiden können, wenn er sich an die Worte seines Lehrmeisters Brecht erinnert hätte.
...\ Dabei wissen wir doch:\ Auch der Hass gegen die Niedrigkeit\ verzerrt die Züge.\ Auch der Zorn über das Unrecht\ Macht die Stimme heiser. Ach, wir\ Die wir den Boden bereiten wollten für die Freundlichkeit\ Konnten selber nicht freundlich sein.\ ...

Er hätte auch von der Medizin nehmen können, die er selbst für andere entwickelt hat \ (1966 für seinen Freund Peter Huchel).
…\ Du, laß dich nicht verhärten\ in dieser harten Zeit.\ Die allzu hart sind, brechen,\ die allzu spitz sind, stechen\ und brechen ab sogleich.\ …
PS: Fortsetzung folgt in der Reihe \ “Was wir von großen Persönlichkeiten lernen können, wenn wir ihnen zuhören würden."
-
 @ 3283ef81:0a531a33
2025-05-24 20:36:35
@ 3283ef81:0a531a33
2025-05-24 20:36:35Suspendisse quis rutrum nisi Integer nec augue quis ex euismod blandit ut ac mi
Curabitur suscipit vulputate volutpat Donec ornare, risus non tincidunt malesuada, elit magna feugiat diam, id faucibus libero libero efficitur mauris
-
 @ 4925ea33:025410d8
2025-03-08 00:38:48
@ 4925ea33:025410d8
2025-03-08 00:38:481. O que é um Aromaterapeuta?

O aromaterapeuta é um profissional especializado na prática da Aromaterapia, responsável pelo uso adequado de óleos essenciais, ervas aromáticas, águas florais e destilados herbais para fins terapêuticos.
A atuação desse profissional envolve diferentes métodos de aplicação, como inalação, uso tópico, sempre considerando a segurança e a necessidade individual do cliente. A Aromaterapia pode auxiliar na redução do estresse, alívio de dores crônicas, relaxamento muscular e melhora da respiração, entre outros benefícios.
Além disso, os aromaterapeutas podem trabalhar em conjunto com outros profissionais da saúde para oferecer um tratamento complementar em diversas condições. Como já mencionado no artigo sobre "Como evitar processos alérgicos na prática da Aromaterapia", é essencial ter acompanhamento profissional, pois os óleos essenciais são altamente concentrados e podem causar reações adversas se utilizados de forma inadequada.
2. Como um Aromaterapeuta Pode Ajudar?

Você pode procurar um aromaterapeuta para diferentes necessidades, como:
✔ Questões Emocionais e Psicológicas
Auxílio em momentos de luto, divórcio, demissão ou outras situações desafiadoras.
Apoio na redução do estresse, ansiedade e insônia.
Vale lembrar que, em casos de transtornos psiquiátricos, a Aromaterapia deve ser usada como terapia complementar, associada ao tratamento médico.
✔ Questões Físicas
Dores musculares e articulares.
Problemas respiratórios como rinite, sinusite e tosse.
Distúrbios digestivos leves.
Dores de cabeça e enxaquecas. Nesses casos, a Aromaterapia pode ser um suporte, mas não substitui a medicina tradicional para identificar a origem dos sintomas.
✔ Saúde da Pele e Cabelos
Tratamento para acne, dermatites e psoríase.
Cuidados com o envelhecimento precoce da pele.
Redução da queda de cabelo e controle da oleosidade do couro cabeludo.
✔ Bem-estar e Qualidade de Vida
Melhora da concentração e foco, aumentando a produtividade.
Estímulo da disposição e energia.
Auxílio no equilíbrio hormonal (TPM, menopausa, desequilíbrios hormonais).
Com base nessas necessidades, o aromaterapeuta irá indicar o melhor tratamento, calculando doses, sinergias (combinação de óleos essenciais), diluições e técnicas de aplicação, como inalação, uso tópico ou difusão.
3. Como Funciona uma Consulta com um Aromaterapeuta?

Uma consulta com um aromaterapeuta é um atendimento personalizado, onde são avaliadas as necessidades do cliente para a criação de um protocolo adequado. O processo geralmente segue estas etapas:
✔ Anamnese (Entrevista Inicial)
Perguntas sobre saúde física, emocional e estilo de vida.
Levantamento de sintomas, histórico médico e possíveis alergias.
Definição dos objetivos da terapia (alívio do estresse, melhora do sono, dores musculares etc.).
✔ Escolha dos Óleos Essenciais
Seleção dos óleos mais indicados para o caso.
Consideração das propriedades terapêuticas, contraindicações e combinações seguras.
✔ Definição do Método de Uso
O profissional indicará a melhor forma de aplicação, que pode ser:
Inalação: difusores, colares aromáticos, vaporização.
Uso tópico: massagens, óleos corporais, compressas.
Banhos aromáticos e escalda-pés. Todas as diluições serão ajustadas de acordo com a segurança e a necessidade individual do cliente.
✔ Plano de Acompanhamento
Instruções detalhadas sobre o uso correto dos óleos essenciais.
Orientação sobre frequência e duração do tratamento.
Possibilidade de retorno para ajustes no protocolo.
A consulta pode ser realizada presencialmente ou online, dependendo do profissional.
Quer saber como a Aromaterapia pode te ajudar? Agende uma consulta comigo e descubra os benefícios dos óleos essenciais para o seu bem-estar!
-
 @ 04c915da:3dfbecc9
2025-03-07 00:26:37
@ 04c915da:3dfbecc9
2025-03-07 00:26:37There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ 3f770d65:7a745b24
2025-04-21 00:15:06
@ 3f770d65:7a745b24
2025-04-21 00:15:06At the recent Launch Music Festival and Conference in Lancaster, PA, featuring over 120 musicians across three days, I volunteered my time with Tunestr and Phantom Power Music's initiative to introduce artists to Bitcoin, Nostr, and the value-for-value model. Tunestr sponsored a stage, live-streaming 21 bands to platforms like Tunestr.io, Fountain.fm and other Nostr/Podcasting 2.0 apps and on-boarding as many others as possible at our conference booth. You may have seen me spamming about this over the last few days.
V4V Earnings
Day 1: 180,000 sats
Day 2: 300,000 sats
Day 3: Over 500,000 sats
Who?
Here are the artists that were on-boarded to Fountain and were live streaming on the Value-for-Value stage:
nostr:npub1cruu4z0hwg7n3r2k7262vx8jsmra3xpku85frl5fnfvrwz7rd7mq7e403w nostr:npub12xeh3n7w8700z4tpd6xlhlvg4vtg4pvpxd584ll5sva539tutc3q0tn3tz nostr:npub1rc80p4v60uzfhvdgxemhvcqnzdj7t59xujxdy0lcjxml3uwdezyqtrpe0j @npub16vxr4pc2ww3yaez9q4s53zkejjfd0djs9lfe55sjhnqkh nostr:npub10uspdzg4fl7md95mqnjszxx82ckdly8ezac0t3s06a0gsf4f3lys8ypeak nostr:npub1gnyzexr40qut0za2c4a0x27p4e3qc22wekhcw3uvdx8mwa3pen0s9z90wk nostr:npub13qrrw2h4z52m7jh0spefrwtysl4psfkfv6j4j672se5hkhvtyw7qu0almy nostr:npub1p0kuqxxw2mxczc90vcurvfq7ljuw2394kkqk6gqnn2cq0y9eq5nq87jtkk nostr:npub182kq0sdp7chm67uq58cf4vvl3lk37z8mm5k5067xe09fqqaaxjsqlcazej nostr:npub162hr8kd96vxlanvggl08hmyy37qsn8ehgj7za7squl83um56epnswkr399 nostr:npub17jzk5ex2rafres09c4dnn5mm00eejye6nrurnlla6yn22zcpl7vqg6vhvx nostr:npub176rnksulheuanfx8y8cr2mrth4lh33svvpztggjjm6j2pqw6m56sq7s9vz nostr:npub1akv7t7xpalhsc4nseljs0c886jzuhq8u42qdcwvu972f3mme9tjsgp5xxk nostr:npub18x0gv872489lrczp9d9m4hx59r754x7p9rg2jkgvt7ul3kuqewtqsssn24
Many more musicians were on-boarded to Fountain, however, we were unable to obtain all of their npubs.
THANK YOU TO ALL ZAPPERS AND BOOSTERS!
Musicians “Get It”
My key takeaway was the musicians' absolute understanding that the current digital landscape along with legacy social media is failing them. Every artist I spoke with recognized how algorithms hinder fan connection and how gatekeepers prevent fair compensation for their work. They all use Spotify, but they only do so out of necessity. They felt the music industry is primed for both a social and monetary revolution. Some of them were even speaking my language…
Because of this, concepts like decentralization, censorship resistance, owning your content, and controlling your social graph weren't just understood by them, they were instantly embraced. The excitement was real; they immediately saw the potential and agreed with me. Bitcoin and Nostr felt genuinely punk rock and that helped a lot of them identify with what we were offering them.
The Tools and the Issues
While the Nostr ecosystem offers a wide variety of tools, we focused on introducing three key applications at this event to keep things clear for newcomers:
- Fountain, with a music focus, was the primary tool for onboarding attendees onto Nostr. Fountain was also chosen thanks to Fountain’s built-in Lightning wallet.
- Primal, as a social alternative, was demonstrated to show how users can take their Nostr identity and content seamlessly between different applications.
- Tunestr.io, lastly was showcased for its live video streaming capabilities.
Although we highlighted these three, we did inform attendees about the broader range of available apps and pointed them to
nostrapps.comif they wanted to explore further, aiming to educate without overwhelming them.This review highlights several UX issues with the Fountain app, particularly concerning profile updates, wallet functionality, and user discovery. While Fountain does work well, these minor hiccups make it extremely hard for on-boarding and education.
- Profile Issues:
- When a user edits their profile (e.g., Username/Nostr address, Lightning address) either during or after creation, the changes don't appear to consistently update across the app or sync correctly with Nostr relays.
- Specifically, the main profile display continues to show the old default Username/Nostr address and Lightning address inside Fountain and on other Nostr clients.
- However, the updated Username/Nostr address does appear on https://fountain.fm (chosen-username@fountain.fm) and is visible within the "Edit Profile" screen itself in the app.
- This inconsistency is confusing for users, as they see their updated information in some places but not on their main public-facing profile within the app. I confirmed this by observing a new user sign up and edit their username – the edit screen showed the new name, but the profile display in Fountain did not update and we did not see it inside Primal, Damus, Amethyst, etc.
- Wallet Limitations:
- The app's built-in wallet cannot scan Lightning address QR codes to initiate payments.
- This caused problems during the event where users imported Bitcoin from Azte.co vouchers into their Fountain wallets. When they tried to Zap a band by scanning a QR code on the live tally board, Fountain displayed an error message stating the invoice or QR code was invalid.
- While suggesting musicians install Primal as a second Nostr app was a potential fix for the QR code issue, (and I mentioned it to some), the burden of onboarding users onto two separate applications, potentially managing two different wallets, and explaining which one works for specific tasks creates a confusing and frustrating user experience.
- Search Difficulties:
- Finding other users within the Fountain app is challenging. I was unable to find profiles from brand new users by entering their chosen Fountain username.
- To find a new user, I had to resort to visiting their profile on the web (fountain.fm/username) to retrieve their npub. Then, open Primal and follow them. Finally, when searching for their username, since I was now following them, I was able to find their profile.
- This search issue is compounded by the profile syncing problem mentioned earlier, as even if found via other clients, their displayed information is outdated.
- Searching for the event to Boost/Zap inside Fountain was harder than it should have been the first two days as the live stream did not appear at the top of the screen inside the tap. This was resolved on the third day of the event.
Improving the Onboarding Experience
To better support user growth, educators and on-boarders need more feature complete and user-friendly applications. I love our developers and I will always sing their praises from the highest mountain tops, however I also recognize that the current tools present challenges that hinder a smooth onboarding experience.
One potential approach explored was guiding users to use Primal (including its built-in wallet) in conjunction with Wavlake via Nostr Wallet Connect (NWC). While this could facilitate certain functions like music streaming, zaps, and QR code scanning (which require both Primal and Wavlake apps), Wavlake itself has usability issues. These include inconsistent or separate profiles between web and mobile apps, persistent "Login" buttons even when logged in on the mobile app with a Nostr identity, and the minor inconvenience of needing two separate applications. Although NWC setup is relatively easy and helps streamline the process, the need to switch between apps adds complexity, especially when time is limited and we’re aiming to showcase the benefits of this new system.
Ultimately, we need applications that are more feature-complete and intuitive for mainstream users to improve the onboarding experience significantly.
Looking forward to the future
I anticipate that most of these issues will be resolved when these applications address them in the near future. Specifically, this would involve Fountain fixing its profile issues and integrating Nostr Wallet Connect (NWC) to allow users to utilize their Primal wallet, or by enabling the scanning of QR codes that pay out to Lightning addresses. Alternatively, if Wavlake resolves the consistency problems mentioned earlier, this would also significantly improve the situation giving us two viable solutions for musicians.
My ideal onboarding event experience would involve having all the previously mentioned issues resolved. Additionally, I would love to see every attendee receive a $5 or $10 voucher to help them start engaging with value-for-value, rather than just the limited number we distributed recently. The goal is to have everyone actively zapping and sending Bitcoin throughout the event. Maybe we can find a large sponsor to facilitate this in the future?
What's particularly exciting is the Launch conference's strong interest in integrating value-for-value across their entire program for all musicians and speakers at their next event in Dallas, Texas, coming later this fall. This presents a significant opportunity to onboard over 100+ musicians to Bitcoin and Nostr, which in turn will help onboard their fans and supporters.
We need significantly more zaps and more zappers! It's unreasonable to expect the same dedicated individuals to continuously support new users; they are being bled dry. A shift is needed towards more people using bitcoin for everyday transactions, treating it as money. This brings me back to my ideal onboarding experience: securing a sponsor to essentially give participants bitcoin funds specifically for zapping and tipping artists. This method serves as a practical lesson in using bitcoin as money and showcases the value-for-value principle from the outset.
-
 @ 866e0139:6a9334e5
2025-05-18 21:49:14
@ 866e0139:6a9334e5
2025-05-18 21:49:14Autor: Michael Meyen. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
„Warum der Weltfrieden von Deutschland abhängt“ steht auf dem Cover. Sicher: Ein Verlag will verkaufen. Superlative machen sich da immer gut. Der Weltfrieden und Deutschland. „Wie das“, wird mancher fragen, über den Atlantik schauen, nach Kiew oder gar nach Moskau und nach Peking, und die 24 Euro ausgeben. Ich kann nur sagen: Das ist gut investiert, wenn man verstehen will, was uns die Nachrichtensprecher und ihre Kritiker im Moment alles um die Ohren hauen. Ich durfte die Texte von Hauke Ritz schon lesen und ein Vorwort schreiben, in dem es nicht nur um Krieg und Frieden geht, sondern auch um die Frage, warum sich manche, die einst „links“ zu stehen glaubten, inzwischen mit einigen Konservativen besser vertragen als mit den alten Genossen – nicht nur bei der Gretchenfrage auf dem Cover. Nun aber zu meinem Vorwort.
1. Der Leser
Hauke Ritz hat meinen Blick auf die Welt verändert. In diesem Satz stecken zwei Menschen. Ich fange mit dem Leser an, weil jeder Text auf einen Erfahrungsberg trifft, gewachsen durch all das, was Herkunft, soziale Position und Energievorrat ermöglichen. Ob ein Autor dort auf Resonanz stößt, kann er nicht beeinflussen. Also zunächst etwas zu mir. Ich bin auf der Insel Rügen aufgewachsen – in einer kommunistischen Familie und mit Karl Marx. Das Sein bestimmt das Bewusstsein. In der Schule haben wir Kinder uns über ein anderes Marx-Zitat amüsiert, das in einem der Räume groß an der Wand stand. „Die Philosophen haben die Welt nur verschieden interpretiert, es kömmt drauf an, sie zu verändern.“ Kömmt. Dieser Marx. Was der sich traut.
Das Schulhaus ist nach 1990 schnell abgerissen worden. Bauland mit Meerblick, fünf Minuten bis zum Strand. Marx stand nun zwar kaum noch in der Zeitung, Eltern, Freunde und Bekannte waren sich aber trotzdem sicher, dass er Recht hat. Das Sein bestimmt das Bewusstsein. Hier die Ostdeutschen, auf Jahre gebunden im Kampf um Arbeitsplatz und Qualifikationsnachweise, Rente und Grundstück, und dort Glücksritter aus dem Westen, die sich das Dorf kaufen und nach ihrem Bilde formen. Das Kapital live in Aktion gewissermaßen.
Ich selbst bin damals eher durch Zufall an der Universität gelandet und habe dort eine Spielart der Medienforschung kennengelernt, die in den USA erfunden worden war, um den Zweiten Weltkrieg nicht nur auf dem Schlachtfeld zu gewinnen, sondern auch in den Köpfen. Diese akademische Disziplin konnte und wollte nach ihrer Ankunft in der alten Bundesrepublik nichts mit Marx am Hut haben. Zum einen war da dieser neue Freund auf der anderen Atlantikseite, moralisch sauber und damit ein Garant gegen den Vorwurf, mitgemacht zu haben und vielleicht sogar Goebbels und sein Postulat von den Medien als Führungsmittel immer noch in sich zu tragen. Je lauter dieser Vorwurf wurde, desto stärker zog es deutsche Propagandaforscher, die sich zur Tarnung Kommunikations- oder Publizistikwissenschaftler nannten, in die USA.
Zum anderen verbannte der Radikalenerlass jeden Hauch von Marxismus aus dem universitären Leben. Selbst Postmarxisten wie Adorno und Horkheimer mit ihrer Frankfurter Schule, Karl Mannheim oder Pierre Bourdieu, auf die ich bei der Suche nach einer neuen intellektuellen Heimat fast zwangsläufig gestoßen bin, spielten in den Lehrveranstaltungen kaum eine Rolle und damit auch nicht in Dissertationen, Habilitationen, Fachzeitschriften. Peer Review wird schnell zur Farce, wenn jeder Gutachter weiß, dass bestimmte Texte nur von mir und meinen Schülern zitiert werden. Ich habe dann versucht, die Kollegen mit Foucault zu überraschen, aber auch das hat nicht lange funktioniert.
Zu Hauke Ritz ist es von da immer noch weit. Ich habe eine Lungenembolie gebraucht (2013), zwei Auftritte bei KenFM (2018) und die Attacken, die auf diese beiden Interviews zielten sowie auf meinen Blog Medienrealität, gestartet 2017 und zeitgleich mit großen Abendveranstaltungen aus der virtuellen Welt in die Uni-Wirklichkeit geholt, um bereit zu sein für diesen Denker. Corona nicht zu vergessen. Ich erinnere mich noch genau an diesen Abend. Narrative Nummer 16 im August 2020. Hauke Ritz zu Gast bei Robert Cibis, Filmemacher und Kopf von Ovalmedia. Da saß jemand, der mühelos durch die Geschichte spazierte und es dabei schaffte, geistige und materielle Welt zusammenzubringen. Meine Götter Marx, Bourdieu und Foucault, wenn man so will, angereichert mit mehr als einem Schuss Religionswissen, um die jemand wie ich, als Atheist erzogen und immer noch aufgeregt, wenn er vor einer Kirche steht, eher einen Bogen macht. Dazu all das, was ich in tapsigen Schritten auf dem Gebiet der historischen Forschung zu erkunden versucht hatte – nur in weit längeren Zeiträumen und mit der Vogelperspektive, die jede gute Analyse braucht. Und ich kannte diesen Mann nicht. Ein Armutszeugnis nach mehr als einem Vierteljahrhundert in Bewusstseinsindustrie und Ideologieproduktion.
2. Der Autor
Und damit endlich zu diesem Autor, der meinen Blick auf die Welt verändert hat. Hauke Ritz, Jahrgang 1975, ist ein Kind der alten deutschen Universität. Er hat an der FU Berlin studiert, als man dort noch Professoren treffen konnte, denen Eigenständigkeit wichtiger war als Leistungspunkte, Deadlines und politische Korrektheit. Seine Dissertation wurzelt in diesem ganz anderen akademischen Milieu. Ein dickes Buch, in dem es um Geschichtsphilosophie geht und um die Frage, welchen Reim sich die Deutschen vom Ersten Weltkrieg bis zum Fall der Berliner Mauer auf den Siegeszug von Wissenschaft und Technik gemacht haben. Das klingt sehr akademisch, wird aber schnell politisch, wenn man die Aufsätze liest, die Hauke Ritz ab den späten Nullerjahren auf diesem Fundament aufgebaut hat und die hier nun in einer Art Best-of in die Öffentlichkeit zurückgeholt werden aus dem Halbdunkel von Publikationsorten, deren Reputation inzwischen zum Teil gezielt zerstört worden ist, und die so hoffentlich ein großes und neues Publikum erreichen. In den Texten, die auf dieses Vorwort folgen, geht es um den tiefen Staat und den neuen kalten Krieg, um Geopolitik und Informationskriege und dabei immer wieder auch um die geistige Krise der westlichen Welt sowie um den fehlenden Realitätssinn deutscher Außenpolitik.
Bevor ich darauf zurückkomme, muss ich die Doppelbiografie abrunden, mit der ich eingestiegen bin. Im Februar 2022, wir erinnern uns auch mit Hilfe des Interviews, das Paul Schreyer mit ihm führte, war Hauke Ritz gerade in Moskau, als Universitätslehrer auf Zeit mit einem DAAD-Stipendium. Im November 2024, als ich diese Zeilen schreibe, ist er wieder einmal in China, mit familiären Verbindungen. Das heißt auch: Hauke Ritz hat mehr gesehen, als einem in den Kongresshotels der US-dominierten Forschergemeinschaften je geboten werden kann. Und er muss weder um Zitationen buhlen noch um irgendwelche Fördertöpfe und damit auch nicht um das Wohlwollen von Kollegen.
Ein Lehrstuhl oder eine Dozentenstelle, hat er mir im Frühsommer 2021 auf Usedom erzählt, wo wir uns das erste Mal gesehen haben, so eine ganz normale akademische Karriere sei für ihn nicht in Frage gekommen. Der Publikationsdruck, die Denkschablonen. Lieber ökonomisch unsicher, aber dafür geistig frei. Ich habe mir diesen Satz gemerkt, weil er einen Beamten wie mich zwingt, seinen Lebensentwurf auf den Prüfstand zu stellen. Bin ich beim Lesen, Forschen, Schreiben so unabhängig, wie ich mir das stets einzureden versuche? Wo sind die Grenzen, die eine Universität und all die Zwänge setzen, die mit dem Kampf um Reputation verbunden sind? Und was ist mit dem Lockmittel Pension, das jeder verspielt, der das Schiff vor der Zeit verlassen will?
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes.
Hauke Ritz, das zeigen die zehn Aufsätze, die in diesem Buch versammelt sind, hat alles richtig gemacht. Hier präsentiert sich ein Autor, der „von links“ aufgebrochen ist und sich immer noch so sieht (so beschreibt er das dort, wo es um die aktuelle Theorieschwäche des einst gerade hier so dominanten Lagers geht), aber trotzdem keine Angst hat, für ein Wertesystem zu werben, das eher konservativ wirkt. Herkunft und Familie zum Beispiel. Verankerung und Zugehörigkeit, sowohl geografisch als auch intellektuell. Mehr noch: Wenn ich Hauke Ritz richtig verstanden habe, dann braucht es ein Amalgam aus den Restbeständen der »alten« Linken und dem christlich geprägten Teil des konservativen Lagers, um eine Entwicklung aufzuhalten und vielleicht sogar umzukehren, die in seinen Texten das Etikett »Postmoderne« trägt. Grenzen sprengen, Identitäten schleifen, Traditionen vergessen. Umwertung aller Werte. Transgender und Trans- oder sogar Posthumanismus. Wer all das nicht mag, findet in diesem Buch ein Reiseziel. Gerechtigkeit und Utopie, Wahrheitssuche, der Glaube an die Schöpferkraft des Menschen und die geistige Regulierung politischer Macht – verwurzelt in der Topografie Europas, die Konkurrenz erzwang, und vor allem im Christentum, weitergetragen in weltlichen Religionen wie dem Kommunismus, und so attraktiv, dass Hauke Ritz von Universalismus sprechen kann, von der Fähigkeit dieser Kultur, ein Leitstern für die Welt zu sein.
Ich habe die Texte im Frühling 2022 gelesen, allesamt in einem Rutsch, um mich auf das Gespräch vorzubereiten, das ich mit Hauke Ritz dann im Juni für die Plattform Apolut geführt habe, den Nachfolger von KenFM. Ich weiß, dass das ein Privileg ist. Lesen, worauf man Lust hat, und dafür auch noch bezahlt werden. Ich weiß auch, dass ich ohne die Vorgeschichte, ohne Corona und all das, was mich und dieses Land dorthin geführt hat, niemals das Glück hätte empfinden können, das mit der Entdeckung eines Autors wie Hauke Ritz verbunden ist. Ohne all das wäre ich wahrscheinlich weiter zu irgendwelchen hochwichtigen Tagungen in die USA geflogen und hätte mich mit Aufsätzen für Fachzeitschriften gequält, die für einen winzigen Kreis von Eingeweihten gemacht und selbst von diesem Kreis allenfalls registriert, aber nicht studiert werden.
Lange Gespräche mit Köpfen wie Hauke Ritz hatten bei Ovalmedia oder Apolut in den Coronajahren sechsstellige Zuschauerzahlen. Ein großes Publikum, wenn man die Komplexität und die Originalität mitdenkt, die jeder Leser gleich genießen kann. Man findet diese Videos noch, allerdings nicht beim De-facto-Monopolisten YouTube, der Zensur sei Dank. Im Bermudadreieck zwischen Berlin, Brüssel und dem Silicon Valley verschwindet alles, was die hegemonialen Narrative herausfordert und das Potenzial hat, Menschenmassen erst zu erreichen und dann zu bewegen. Ich habe Hauke Ritz deshalb schon im Studio und am Abend nach unserem Dreh ermutigt und wahrscheinlich sogar ein wenig gedrängt, aus seinen Aufsätzen ein Buch zu machen. Das war auch ein wenig egoistisch gedacht: Ich wollte mein Aha-Erlebnis mit anderen teilen und so Gleichgesinnte heranziehen. Der Mensch ist ein Herdentier und mag es nicht, allein und isoliert zu sein.
3. Ein neuer Blick auf Macht
Drei Jahre später gibt es nicht nur die Aufsatzsammlung, die Sie gerade in den Händen halten, sondern auch ein Buch, das ich als „großen Wurf“ beschrieben habe – als Werk eines Autors, der die Wirklichkeit nicht ignoriert (Geografie, Reichtum und die Geschichte mit ihren ganz realen Folgen), sich aber trotzdem von der Vorstellung löst, dass der Mensch in all seinem Streben und Irren nicht mehr sei als ein Produkt der Umstände. Hauke Ritz dreht den Spieß um: Die Geschichte bewegt nicht uns, sondern wir bewegen sie. Was passiert, das passiert auch und vielleicht sogar in erster Linie, weil wir ganz bestimmte Vorstellungen von der Vergangenheit und unserem Platz in dieser Welt verinnerlicht haben. Von diesem Axiom ist es nur ein klitzekleiner Schritt zur Machtpolitik: Wenn es stimmt, dass das historische Bewusstsein mindestens genauso wichtig ist wie Atomsprengköpfe, Soldaten oder Gasfelder, dann können sich die Geheimdienste nicht auf Überwachung und Kontrolle beschränken. Dann müssen sie in die Ideenproduktion eingreifen. Und wir? Wir müssen die Geistesgeschichte neu schreiben, Politik anders sehen und zuallererst begreifen, dass der Mensch das Sein verändern kann, wenn er denn versteht, wer und was seinen Blick bisher gelenkt hat. Ich bin deshalb besonders froh, dass es auch das Herz der Serie „Die Logik des neuen kalten Krieges“ in dieses Buch geschafft hat, ursprünglich 2016 bei RT-Deutsch erschienen. Diese Stücke sind exemplarisch für das Denken von Hauke Ritz. Der Neoliberalismus, um das nur an einem Beispiel zu illustrieren, wird dort von ihm nicht ökonomisch interpretiert, „sondern als ein Kulturmodell“, das zu verstehen hilft, wie es zu der Ehe von Kapitalismus und „neuer Linker“ kommen konnte und damit sowohl zu jener „aggressiven Dominanz des Westens“, die auch den Westend-Verlag umtreibt und so diese Publikation ermöglicht, als auch zur „Vernachlässigung der sozialen Frage“.
Hauke Ritz holt die geistige Dimension von Herrschen und Beherrschtwerden ins Scheinwerferlicht und fragt nach der „Macht des Konzepts“. Diese Macht, sagt Hauke Ritz nicht nur in seinem Aufsatz über die „kulturelle Dimension des Kalten Krieges“, hat 1989/90 den Zweikampf der Systeme entschieden. Nicht die Ökonomie, nicht das Wohlstandsgefälle, nicht das Wettrüsten. Ein Riesenreich wie die Sowjetunion, kaum verschuldet, autark durch Rohstoffe und in der Lage, jeden Feind abzuschrecken, habe weder seine Satellitenstaaten aufgeben müssen noch sich selbst – wenn da nicht der Sog gewesen wäre, der von der Rockmusik ausging, von Jeans und Hollywood, von bunten Schaufenstern und von einem Märchen, das das andere Lager als Hort von Mitbestimmung, Pressefreiheit und ganz privatem Glück gepriesen hat. Als selbst der erste Mann im Kreml all das für bare Münze nahm und Glasnost ausrief (das, was der Westen für seinen Journalismus bis heute behauptet, aber schon damals nicht einlösen konnte und wollte), sei es um den Gegenentwurf geschehen gewesen. Die Berliner Mauer habe der Psychologie nicht standhalten können.
Fast noch wichtiger: All das war kein Zufall, sondern Resultat strategischer und vor allem geheimdienstlicher Arbeit. Hauke Ritz kann sich hier unter anderem auf Francis Stonor Saunders und Michael Hochgeschwender stützen und so herausarbeiten, wie die CIA über den Kongress für kulturelle Freiheit in den 1950ern und 1960ern Schriftsteller und Journalisten finanzierte, Musiker und Maler, Zeitschriften, Galerien, Filme – und damit Personal, Denkmuster, Symbole. Die „neue“ Linke, „nicht-kommunistisch“, also nicht mehr an der System- und Eigentumsfrage interessiert, diese „neue“ Linke ist, das lernen wir bei Hauke Ritz, genauso ein Produkt von Ideenmanagement wie das positive US-Bild vieler Westeuropäer oder eine neue französische Philosophie um Michel Foucault, Claude Lévi-Strauss oder Bernard-Henri Lévy, die Marx und Hegel abwählte, stattdessen auf Nietzsche setzte und so ein Fundament schuf für das „Projekt einer Umwertung aller Werte“.
Natürlich kann man fragen: Was hat all das mit uns zu tun? Mit dem Krieg in der Ukraine, mit der Zukunft Europas oder gar mit der These auf dem Buchcover, dass nichts weniger als der „Weltfrieden“ ausgerechnet von uns, von Deutschland abhängt? Warum sollen wir uns mit Kämpfen in irgendwelchen Studierstübchen beschäftigen, die höchstens zwei Handvoll Gelehrte verstehen? Hauke Ritz sagt: Wer die Welt beherrschen will, muss den Code der europäischen Kultur umschreiben. Wie weit dieses „Projekt“ schon gediehen ist, sieht jeder, der die Augen öffnet. In der Lesart von Hauke Ritz ist Europa Opfer einer „postmodernen Fehlinterpretation seiner eigenen Kultur“, importiert aus den USA und nur abzuwehren mit Hilfe von Russland, das zwar zu Europa gehöre, sich vom Westen des Kontinents aber unterscheide und deshalb einen Gegenentwurf liefern könne. Stichworte sind hier Orthodoxie und Sozialismus sowie eine Vergangenheit als Imperium, ohne die, so sieht das Hauke Ritz, neben diplomatischen Erfahrungen die „politischen Energien“ fehlen, die nötig sind, um Souveränität auch da zu bewahren, wo die „Macht des Konzepts“ beginnt. China und der Iran ja, Indien und Lateinamerika nein.
Keine Angst, ich schreibe hier kein zweites Buch. Diese Appetithäppchen sollen Lust machen auf einen Autor, der die Hektik der Gegenwart hinter sich lässt und aus den Tiefen der Geschichte eine Interpretation anbietet, die die hegemoniale Ideologie in ein ganz neues Licht rückt und sie so als „Rechtfertigungslehre“ enttarnt (Werner Hofmann) oder als „Machtinterpretation der Wirklichkeit“ (Václav Havel), die sich zwangsläufig „ritualisiert“ und „von der Wirklichkeit emanzipiert“, um als „Alibi“ für alle funktionieren zu können, die mit der Macht marschieren. Ich weiß nicht mehr, wie ich das Marx-Zitat mit dem komischen Wort „kömmt“ als kleiner Junge gedeutet habe. Ich wusste wenig von Philosophie und gar nichts von der Welt. Hauke Ritz blickt nicht nur in Abgründe, die ich vorher allenfalls aus dem Augenwinkel gesehen hatte, sondern bietet zugleich eine Lösung an. Als Gleichung und in seinen Worten formuliert: „klassische Arbeiterbewegung“ plus „christlich orientierte Wertkonservative“ ist gleich Hoffnung und Neustart. Und nun Vorhang auf für einen Philosophen, der nicht nur Deutschland einen Weg weist in Richtung Veränderung und Frieden.
Michael Meyen ist Medienforscher, Ausbilder und Journalist. Seit 2002 ist er Universitätsprofessor an der LMU München. https://www.freie-medienakademie.de/
Der Link zum Buch von Hauke Ritz
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 6e0ea5d6:0327f353
2025-02-21 18:15:52
@ 6e0ea5d6:0327f353
2025-02-21 18:15:52"Malcolm Forbes recounts that a lady, wearing a faded cotton dress, and her husband, dressed in an old handmade suit, stepped off a train in Boston, USA, and timidly made their way to the office of the president of Harvard University. They had come from Palo Alto, California, and had not scheduled an appointment. The secretary, at a glance, thought that those two, looking like country bumpkins, had no business at Harvard.
— We want to speak with the president — the man said in a low voice.
— He will be busy all day — the secretary replied curtly.
— We will wait.
The secretary ignored them for hours, hoping the couple would finally give up and leave. But they stayed there, and the secretary, somewhat frustrated, decided to bother the president, although she hated doing that.
— If you speak with them for just a few minutes, maybe they will decide to go away — she said.
The president sighed in irritation but agreed. Someone of his importance did not have time to meet people like that, but he hated faded dresses and tattered suits in his office. With a stern face, he went to the couple.
— We had a son who studied at Harvard for a year — the woman said. — He loved Harvard and was very happy here, but a year ago he died in an accident, and we would like to erect a monument in his honor somewhere on campus.— My lady — said the president rudely —, we cannot erect a statue for every person who studied at Harvard and died; if we did, this place would look like a cemetery.
— Oh, no — the lady quickly replied. — We do not want to erect a statue. We would like to donate a building to Harvard.
The president looked at the woman's faded dress and her husband's old suit and exclaimed:
— A building! Do you have even the faintest idea of how much a building costs? We have more than seven and a half million dollars' worth of buildings here at Harvard.
The lady was silent for a moment, then said to her husband:
— If that’s all it costs to found a university, why don’t we have our own?
The husband agreed.
The couple, Leland Stanford, stood up and left, leaving the president confused. Traveling back to Palo Alto, California, they established there Stanford University, the second-largest in the world, in honor of their son, a former Harvard student."
Text extracted from: "Mileumlivros - Stories that Teach Values."
Thank you for reading, my friend! If this message helped you in any way, consider leaving your glass “🥃” as a token of appreciation.
A toast to our family!
-
 @ 6389be64:ef439d32
2025-02-27 21:32:12
@ 6389be64:ef439d32
2025-02-27 21:32:12GA, plebs. The latest episode of Bitcoin And is out, and, as always, the chicanery is running rampant. Let’s break down the biggest topics I covered, and if you want the full, unfiltered rant, make sure to listen to the episode linked below.
House Democrats’ MEME Act: A Bad Joke?
House Democrats are proposing a bill to ban presidential meme coins, clearly aimed at Trump’s and Melania’s ill-advised token launches. While grifters launching meme coins is bad, this bill is just as ridiculous. If this legislation moves forward, expect a retaliatory strike exposing how politicians like Pelosi and Warren mysteriously amassed their fortunes. Will it pass? Doubtful. But it’s another sign of the government’s obsession with regulating everything except itself.
Senate Banking’s First Digital Asset Hearing: The Real Target Is You
Cynthia Lummis chaired the first digital asset hearing, and—surprise!—it was all about control. The discussion centered on stablecoins, AML, and KYC regulations, with witnesses suggesting Orwellian measures like freezing stablecoin transactions unless pre-approved by authorities. What was barely mentioned? Bitcoin. They want full oversight of stablecoins, which is really about controlling financial freedom. Expect more nonsense targeting self-custody wallets under the guise of stopping “bad actors.”
Bank of America and PayPal Want In on Stablecoins
Bank of America’s CEO openly stated they’ll launch a stablecoin as soon as regulation allows. Meanwhile, PayPal’s CEO paid for a hat using Bitcoin—not their own stablecoin, Pi USD. Why wouldn’t he use his own product? Maybe he knows stablecoins aren’t what they’re hyped up to be. Either way, the legacy financial system is gearing up to flood the market with stablecoins, not because they love crypto, but because it’s a tool to extend U.S. dollar dominance.
MetaPlanet Buys the Dip
Japan’s MetaPlanet issued $13.4M in bonds to buy more Bitcoin, proving once again that institutions see the writing on the wall. Unlike U.S. regulators who obsess over stablecoins, some companies are actually stacking sats.
UK Expands Crypto Seizure Powers
Across the pond, the UK government is pushing legislation to make it easier to seize and destroy crypto linked to criminal activity. While they frame it as going after the bad guys, it’s another move toward centralized control and financial surveillance.
Bitcoin Tools & Tech: Arc, SatoChip, and Nunchuk
Some bullish Bitcoin developments: ARC v0.5 is making Bitcoin’s second layer more efficient, SatoChip now supports Taproot and Nostr, and Nunchuk launched a group wallet with chat, making multisig collaboration easier.
The Bottom Line
The state is coming for financial privacy and control, and stablecoins are their weapon of choice. Bitcoiners need to stay focused, keep their coins in self-custody, and build out parallel systems. Expect more regulatory attacks, but don’t let them distract you—just keep stacking and transacting in ways they can’t control.
🎧 Listen to the full episode here: https://fountain.fm/episode/PYITCo18AJnsEkKLz2Ks
💰 Support the show by boosting sats on Podcasting 2.0! and I will see you on the other side.
-
 @ 6c05c73e:c4356f17
2025-05-24 19:16:17
@ 6c05c73e:c4356f17
2025-05-24 19:16:17Descrição da empresa
Fundada em 1961, a WEG é uma empresa global de equipamentos eletroeletrônicos, atuando principalmente no setor de bens de capital com soluções em máquinas elétricas, automação e tintas, para diversos setores, incluindo infraestrutura, siderurgia, papel e celulose, petróleo e gás, mineração, entre muitos outros.
A WEG se destaca em inovação pelo desenvolvimento constante de soluções para atender as grandes tendências voltadas a eficiência energética, energias renováveis e mobilidade elétrica. Com operações industriais em 17 países e presença comercial em mais de 135 países, a companhia possui mais de 47.000 mil colaboradores distribuídos pelo mundo.
Em 2024, a WEG atingiu faturamento líquido de R$38,0 bilhões, destes 57,0% proveniente das vendas realizadas fora do Brasil.
Vendendo soluções para os clientes
"Na febre do ouro, muito garimpeiros corriam atrás de ouro para ficar ricos. Enquanto isso, muita gente enriqueceu vendendo pás, roupas, bebidas, cigarros e mantimentos para eles…”
Em um mundo dominado cada vez mais por Inteligência Artificial, carros elétricos e tecnologias quânticas. A Wege segue se destacando por oferecer equipamentos e parte da estrutura pode detrás para que essas tecnologias possam existir. Focada em inovação e performance. A empresa oferece soluções de ponta a ponta para os mais variados setores da indústria.
Visão geral da empresa
A Wege atua no setor de máquinas e equipamentos. Se formos fazer um refino, podemos dizer que ela atua em subsetores tais como: motores, compressores e outros.
Mercado que atua
O setor de máquinas e equipamentos no Brasil em 2024 enfrentou um cenário desafiador, com uma queda na receita líquida, mas também mostrou sinais de recuperação e algumas perspectivas positivas em segmentos específicos e no início de 2025.
A WEG é gigante no mundo todo. Os caras têm fábricas e filiais em mais de 40 países, espalhados por todos os continentes. A estratégia dos caras é expandir sempre, comprando outras empresas e investindo pesado em mercados-chave. A empresa foca em: Expansão, inovação e sustentabilidade.
Mercado
Grana Alta: Em 2024, o mercado global de máquinas e equipamentos valeu uns US$ 205,67 bilhões. Já a parte de motores elétricos, chegou a uns US$ 152,2 bilhões. A parada é que a automação industrial, que é a cara do futuro, estava em uns US$ 192,02 bilhões em 2024. É muita grana rolando!
As empresas estão investindo cada vez mais em IA (Inteligência artificial), IOT (internet das coisas, robótica e fabricação sustentável.
Perspectiva de crescimento A parada é que esse mercado tá com gás total pra crescer nos próximos anos, parceiro:
Máquinas e Equipamentos: A expectativa é que o mercado global de máquinas e equipamentos cresça cerca de 6,57% ao ano até 2033, podendo chegar a uns US$ 364,66 bilhões.
Motores Elétricos: Esse setor tá prometendo um crescimento de uns 6,3% ao ano até 2029, podendo bater uns US$ 206,4 bilhões. A demanda por carros elétricos tá puxando muito esse crescimento.
Automação Industrial: Essa é a cereja do bolo! A expectativa é que o mercado de automação industrial dispare uns 9,1% ao ano até 2033, alcançando uns US$ 420,49 bilhões. A busca por mais produtividade, menos erros e mais eficiência tá impulsionando essa onda.
Materia sobre carros eletricos
Oportunidades que o ativo traz
Na minha visão, as maiores oportunidades que a Wege nos traz são:
-
Equipamentos Eletroeletrônicos Industriais
Esta área inclui os motores elétricos, drives e equipamentos e serviços de automação industrial e serviços de manutenção. Os motores elétricos e demais equipamentos têm aplicação em praticamente todos os segmentos industriais, em equipamentos como compressores, bombas e ventiladores.
-
Geração Transmissão e Distribuição de Energia (GTD)
Os produtos e serviços incluídos nesta área são os geradores elétricos para usinas hidráulicas e térmicas (biomassa), turbinas hidráulicas (PCH e CGH), aerogeradores, transformadores, subestações, painéis de controle e serviços de integração de sistemas.
-
Motores Comerciais e Appliance
O foco de atuação nesta área é o mercado de motores monofásicos para bens de consumo durável, como lavadoras de roupas, aparelhos de ar condicionado, bombas de água, entre outros.
Desde Janeiro/25, podemos observar que o gráfico teve uma queda no seu preço. Contudo, continua se mantendo acima da ema200 e com ótimo volume negociado. Isso tudo caracteriza que a tendência majoritária ainda é compradora. Então, devemos pensar em atuar somente nesse sentido.
Riscos
Os maiores riscos que vejo hoje, para uma empresa tão sólida como Wege são:
- Instabilidade Econômica Global e Regional, qualquer flutuação em mercado chave atuante pode representar um risco.
- Inflação e Custo de Insumos, principalmente aço e cobre que são matérias prima base.
- Políticas Tarifárias e Protecionismo, se o homem laranja dos EUA impor tarifas. Pode afetar sim os negócios da empresa como um todo.
Catalisadores
Na minha visão, os catalisadores da empresa. Que impulsionam e continuaram dando força a ela são:
- Forte diversificação de receita, 53% vem em dólar.
- Boa perspectiva do aumento do valor do dólar. Isso representa mais caixa.
- As aquisiçõess feitas recentemente, que vão impulsionar a receita da empresa.
Faq
Qual foi o desempenho da WEGE3 nas últimas 52 semanas?
13.95% foi desempenho das ações da WEGE3 até o momento.
WEGE3 paga dividendos? Qual o Dividend Yield (DY) da WEGE3?
Sim, WEGE3 (WEG) paga dividendos e juros sobre capital próprio (JCP). O Dividend Yield (DY) da WEGE3 tem variado ao longo do tempo, mas geralmente se encontra entre 1,4% e 1,8%, dependendo da cotação atual das ações e dos valores de dividendos e JCP distribuídos.
O que é a WEG? Qual o setor de atuação da WEG?
A WEG é uma empresa global de equipamentos eletroeletrônicos, que atua principalmente no setor de bens de capital. A empresa se destaca por suas soluções em máquinas elétricas, automação, tintas e sistemas de energia, com foco em eficiência energética e sustentabilidade.
Quais produtos a WEG fabrica?
A WEG produz uma vasta gama de produtos e soluções, abrangendo desde equipamentos elétricos e eletrônicos até tintas e vernizes.
Qual é o P/L (Preço sobre Lucro) da WEGE3?
O P/L (Preço sobre Lucro) da WEGE3, conforme indicadores de mercado, está em torno de 29,32.
Bio
Investir não precisa ser um bicho de sete cabeças! Na Threedolar, democratizamos o acesso ao mundo dos investimentos, oferecendo conteúdo claro e prático. Comece hoje mesmo a construir seu futuro financeiro!
Disclaimer
Lembre-se: este não é um conselho de investimento. Faça sua própria pesquisa antes de investir. Resultados passados não garantem lucros futuros. Cuide do seu dinheiro!
Referencia
https://www.fundamentus.com.br/detalhes.php?papel=WEGE3&h=1
https://ri.weg.net/a-weg/perfil-corporativo/
https://ri.weg.net/a-weg/por-que-a-weg/
https://www.cnnbrasil.com.br/auto/carros-eletrificados-registram-85-de-aumento-nas-vendas-de-2024/
-
-
 @ 460c25e6:ef85065c
2025-02-25 15:20:39
@ 460c25e6:ef85065c
2025-02-25 15:20:39If you don't know where your posts are, you might as well just stay in the centralized Twitter. You either take control of your relay lists, or they will control you. Amethyst offers several lists of relays for our users. We are going to go one by one to help clarify what they are and which options are best for each one.
Public Home/Outbox Relays
Home relays store all YOUR content: all your posts, likes, replies, lists, etc. It's your home. Amethyst will send your posts here first. Your followers will use these relays to get new posts from you. So, if you don't have anything there, they will not receive your updates.
Home relays must allow queries from anyone, ideally without the need to authenticate. They can limit writes to paid users without affecting anyone's experience.
This list should have a maximum of 3 relays. More than that will only make your followers waste their mobile data getting your posts. Keep it simple. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of all your content in a place no one can delete. Go to relay.tools and never be censored again. - 1 really fast relay located in your country: paid options like http://nostr.wine are great
Do not include relays that block users from seeing posts in this list. If you do, no one will see your posts.
Public Inbox Relays
This relay type receives all replies, comments, likes, and zaps to your posts. If you are not getting notifications or you don't see replies from your friends, it is likely because you don't have the right setup here. If you are getting too much spam in your replies, it's probably because your inbox relays are not protecting you enough. Paid relays can filter inbox spam out.
Inbox relays must allow anyone to write into them. It's the opposite of the outbox relay. They can limit who can download the posts to their paid subscribers without affecting anyone's experience.
This list should have a maximum of 3 relays as well. Again, keep it small. More than that will just make you spend more of your data plan downloading the same notifications from all these different servers. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of your notifications, invites, cashu tokens and zaps. - 1 really fast relay located in your country: go to nostr.watch and find relays in your country
Terrible options include: - nostr.wine should not be here. - filter.nostr.wine should not be here. - inbox.nostr.wine should not be here.
DM Inbox Relays
These are the relays used to receive DMs and private content. Others will use these relays to send DMs to you. If you don't have it setup, you will miss DMs. DM Inbox relays should accept any message from anyone, but only allow you to download them.
Generally speaking, you only need 3 for reliability. One of them should be a personal relay to make sure you have a copy of all your messages. The others can be open if you want push notifications or closed if you want full privacy.
Good options are: - inbox.nostr.wine and auth.nostr1.com: anyone can send messages and only you can download. Not even our push notification server has access to them to notify you. - a personal relay to make sure no one can censor you. Advanced settings on personal relays can also store your DMs privately. Talk to your relay operator for more details. - a public relay if you want DM notifications from our servers.
Make sure to add at least one public relay if you want to see DM notifications.
Private Home Relays
Private Relays are for things no one should see, like your drafts, lists, app settings, bookmarks etc. Ideally, these relays are either local or require authentication before posting AND downloading each user\'s content. There are no dedicated relays for this category yet, so I would use a local relay like Citrine on Android and a personal relay on relay.tools.
Keep in mind that if you choose a local relay only, a client on the desktop might not be able to see the drafts from clients on mobile and vice versa.
Search relays:
This is the list of relays to use on Amethyst's search and user tagging with @. Tagging and searching will not work if there is nothing here.. This option requires NIP-50 compliance from each relay. Hit the Default button to use all available options on existence today: - nostr.wine - relay.nostr.band - relay.noswhere.com
Local Relays:
This is your local storage. Everything will load faster if it comes from this relay. You should install Citrine on Android and write ws://localhost:4869 in this option.
General Relays:
This section contains the default relays used to download content from your follows. Notice how you can activate and deactivate the Home, Messages (old-style DMs), Chat (public chats), and Global options in each.
Keep 5-6 large relays on this list and activate them for as many categories (Home, Messages (old-style DMs), Chat, and Global) as possible.
Amethyst will provide additional recommendations to this list from your follows with information on which of your follows might need the additional relay in your list. Add them if you feel like you are missing their posts or if it is just taking too long to load them.
My setup
Here's what I use: 1. Go to relay.tools and create a relay for yourself. 2. Go to nostr.wine and pay for their subscription. 3. Go to inbox.nostr.wine and pay for their subscription. 4. Go to nostr.watch and find a good relay in your country. 5. Download Citrine to your phone.
Then, on your relay lists, put:
Public Home/Outbox Relays: - nostr.wine - nos.lol or an in-country relay. -
.nostr1.com Public Inbox Relays - nos.lol or an in-country relay -
.nostr1.com DM Inbox Relays - inbox.nostr.wine -
.nostr1.com Private Home Relays - ws://localhost:4869 (Citrine) -
.nostr1.com (if you want) Search Relays - nostr.wine - relay.nostr.band - relay.noswhere.com
Local Relays - ws://localhost:4869 (Citrine)
General Relays - nos.lol - relay.damus.io - relay.primal.net - nostr.mom
And a few of the recommended relays from Amethyst.
Final Considerations
Remember, relays can see what your Nostr client is requesting and downloading at all times. They can track what you see and see what you like. They can sell that information to the highest bidder, they can delete your content or content that a sponsor asked them to delete (like a negative review for instance) and they can censor you in any way they see fit. Before using any random free relay out there, make sure you trust its operator and you know its terms of service and privacy policies.
-
 @ 9e69e420:d12360c2
2025-02-14 18:07:10
@ 9e69e420:d12360c2
2025-02-14 18:07:10Vice President J.D. Vance addressed the Munich Security Conference, criticizing European leaders for undermining free speech and traditional values. He claimed that the biggest threat to Europe is not from external enemies but from internal challenges. Vance condemned the arrest of a British man for praying near an abortion clinic and accused European politicians of censorship.
He urged leaders to combat illegal immigration and questioned their democratic practices. “There is a new sheriff in town,” he said, referring to President Trump. Vance's remarks were unexpected, as many anticipated discussions on security or Ukraine. His speech emphasized the need for Europe to share the defense burden to ensure stability and security.