-
 @ 21335073:a244b1ad
2025-05-21 16:58:36
@ 21335073:a244b1ad
2025-05-21 16:58:36The other day, I had the privilege of sitting down with one of my favorite living artists. Our conversation was so captivating that I felt compelled to share it. I’m leaving his name out for privacy.
Since our last meeting, I’d watched a documentary about his life, one he’d helped create. I told him how much I admired his openness in it. There’s something strange about knowing intimate details of someone’s life when they know so little about yours—it’s almost like I knew him too well for the kind of relationship we have.
He paused, then said quietly, with a shy grin, that watching the documentary made him realize how “odd and eccentric” he is. I laughed and told him he’s probably the sanest person I know. Because he’s lived fully, chasing love, passion, and purpose with hardly any regrets. He’s truly lived.
Today, I turn 44, and I’ll admit I’m a bit eccentric myself. I think I came into the world this way. I’ve made mistakes along the way, but I carry few regrets. Every misstep taught me something. And as I age, I’m not interested in blending in with the world—I’ll probably just lean further into my own brand of “weird.” I want to live life to the brim. The older I get, the more I see that the “normal” folks often seem less grounded than the eccentric artists who dare to live boldly. Life’s too short to just exist, actually live.
I’m not saying to be strange just for the sake of it. But I’ve seen what the crowd celebrates, and I’m not impressed. Forge your own path, even if it feels lonely or unpopular at times.
It’s easy to scroll through the news and feel discouraged. But actually, this is one of the most incredible times to be alive! I wake up every day grateful to be here, now. The future is bursting with possibility—I can feel it.
So, to my fellow weirdos on nostr: stay bold. Keep dreaming, keep pushing, no matter what’s trending. Stay wild enough to believe in a free internet for all. Freedom is radical—hold it tight. Live with the soul of an artist and the grit of a fighter. Thanks for inspiring me and so many others to keep hoping. Thank you all for making the last year of my life so special.
-
 @ 51bbb15e:b77a2290
2025-05-21 00:24:36
@ 51bbb15e:b77a2290
2025-05-21 00:24:36Yeah, I’m sure everything in the file is legit. 👍 Let’s review the guard witness testimony…Oh wait, they weren’t at their posts despite 24/7 survellience instructions after another Epstein “suicide” attempt two weeks earlier. Well, at least the video of the suicide is in the file? Oh wait, a techical glitch. Damn those coincidences!
At this point, the Trump administration has zero credibility with me on anything related to the Epstein case and his clients. I still suspect the administration is using the Epstein files as leverage to keep a lot of RINOs in line, whereas they’d be sabotaging his agenda at every turn otherwise. However, I just don’t believe in ends-justify-the-means thinking. It’s led almost all of DC to toss out every bit of the values they might once have had.
-
 @ c9badfea:610f861a
2025-05-20 19:49:20
@ c9badfea:610f861a
2025-05-20 19:49:20- Install Sky Map (it's free and open source)
- Launch the app and tap Accept, then tap OK
- When asked to access the device's location, tap While Using The App
- Tap somewhere on the screen to activate the menu, then tap ⁝ and select Settings
- Disable Send Usage Statistics
- Return to the main screen and enjoy stargazing!
ℹ️ Use the 🔍 icon in the upper toolbar to search for a specific celestial body, or tap the 👁️ icon to activate night mode
-
 @ 04c915da:3dfbecc9
2025-05-20 15:53:48
@ 04c915da:3dfbecc9
2025-05-20 15:53:48This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ 04c915da:3dfbecc9
2025-05-20 15:47:16
@ 04c915da:3dfbecc9
2025-05-20 15:47:16Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 3283ef81:0a531a33
2025-05-24 18:17:22
@ 3283ef81:0a531a33
2025-05-24 18:17:22Vestibulum a nunc a sapien aliquam rhoncus\ Sed sem turpis, scelerisque sed augue ut, faucibus blandit lectus
Maecenas commodo, augue in placerat lacinia, lorem libero convallis mi, eu fringilla velit arcu id sem. In ac metus vitae sapien dignissim luctus
-
 @ 6ad3e2a3:c90b7740
2025-05-20 13:49:50
@ 6ad3e2a3:c90b7740
2025-05-20 13:49:50I’ve written about MSTR twice already, https://www.chrisliss.com/p/mstr and https://www.chrisliss.com/p/mstr-part-2, but I want to focus on legendary short seller James Chanos’ current trade wherein he buys bitcoin (via ETF) and shorts MSTR, in essence to “be like Mike” Saylor who sells MSTR shares at the market and uses them to add bitcoin to the company’s balance sheet. After all, if it’s good enough for Saylor, why shouldn’t everyone be doing it — shorting a company whose stock price is more than 2x its bitcoin holdings and using the proceeds to buy the bitcoin itself?
Saylor himself has said selling shares at 2x NAV (net asset value) to buy bitcoin is like selling dollars for two dollars each, and Chanos has apparently decided to get in while the getting (market cap more than 2x net asset value) is good. If the price of bitcoin moons, sending MSTR’s shares up, you are more than hedged in that event, too. At least that’s the theory.
The problem with this bet against MSTR’s mNAV, i.e., you are betting MSTR’s market cap will converge 1:1 toward its NAV in the short and medium term is this trade does not exist in a vacuum. Saylor has described how his ATM’s (at the market) sales of shares are accretive in BTC per share because of this very premium they carry. Yes, we’ll dilute your shares of the company, but because we’re getting you 2x the bitcoin per share, you are getting an ever smaller slice of an ever bigger overall pie, and the pie is growing 2x faster than your slice is reducing. (I https://www.chrisliss.com/p/mstr how this works in my first post.)
But for this accretion to continue, there must be a constant supply of “greater fools” to pony up for the infinitely printable shares which contain only half their value in underlying bitcoin. Yes, those shares will continue to accrete more BTC per share, but only if there are more fools willing to make this trade in the future. So will there be a constant supply of such “fools” to keep fueling MSTR’s mNAV multiple indefinitely?
Yes, there will be in my opinion because you have to look at the trade from the prospective fools’ perspective. Those “fools” are not trading bitcoin for MSTR, they are trading their dollars, selling other equities to raise them maybe, but in the end it’s a dollars for shares trade. They are not selling bitcoin for them.
You might object that those same dollars could buy bitcoin instead, so they are surely trading the opportunity cost of buying bitcoin for them, but if only 5-10 percent of the market (or less) is buying bitcoin itself, the bucket in which which those “fools” reside is the entire non-bitcoin-buying equity market. (And this is not considering the even larger debt market which Saylor has yet to tap in earnest.)
So for those 90-95 percent who do not and are not presently planning to own bitcoin itself, is buying MSTR a fool’s errand, so to speak? Not remotely. If MSTR shares are infinitely printable ATM, they are still less so than the dollar and other fiat currencies. And MSTR shares are backed 2:1 by bitcoin itself, while the fiat currencies are backed by absolutely nothing. So if you hold dollars or euros, trading them for MSTR shares is an errand more sage than foolish.
That’s why this trade (buying BTC and shorting MSTR) is so dangerous. Not only are there many people who won’t buy BTC buying MSTR, there are many funds and other investment entities who are only able to buy MSTR.
Do you want to get BTC at 1:1 with the 5-10 percent or MSTR backed 2:1 with the 90-95 percent. This is a bit like medical tests that have a 95 percent accuracy rate for an asymptomatic disease that only one percent of the population has. If someone tests positive, it’s more likely to be a false one than an indication he has the disease*. The accuracy rate, even at 19:1, is subservient to the size of the respective populations.
At some point this will no longer be the case, but so long as the understanding of bitcoin is not widespread, so long as the dollar is still the unit of account, the “greater fools” buying MSTR are still miles ahead of the greatest fools buying neither, and the stock price and mNAV should only increase.
. . .
One other thought: it’s more work to play defense than offense because the person on offense knows where he’s going, and the defender can only react to him once he moves. Similarly, Saylor by virtue of being the issuer of the shares knows when more will come online while Chanos and other short sellers are borrowing them to sell in reaction to Saylor’s strategy. At any given moment, Saylor can pause anytime, choosing to issue convertible debt or preferred shares with which to buy more bitcoin, and the shorts will not be given advance notice.
If the price runs, and there is no ATM that week because Saylor has stopped on a dime, so to speak, the shorts will be left having to scramble to change directions and buy the shares back to cover. Their momentum might be in the wrong direction, though, and like Allen Iverson breaking ankles with a crossover, Saylor might trigger a massive short squeeze, rocketing the share price ever higher. That’s why he actually welcomes Chanos et al trying this copycat strategy — it becomes the fuel for outsized gains.
For that reason, news that Chanos is shorting MSTR has not shaken my conviction, though there are other more pertinent https://www.chrisliss.com/p/mstr-part-2 with MSTR, of which one should be aware. And as always, do your own due diligence before investing in anything.
* To understand this, consider a population of 100,000, with one percent having a disease. That means 1,000 have it, 99,000 do not. If the test is 95 percent accurate, and everyone is tested, 950 of the 1,000 will test positive (true positives), 50 who have it will test negative (false negatives.) Of the positives, 95 percent of 99,000 (94,050) will test negative (true negatives) and five percent (4,950) will test positive (false positives). That means 4,950 out of 5,900 positives (84%) will be false.
-
 @ b83a28b7:35919450
2025-05-16 19:26:56
@ b83a28b7:35919450
2025-05-16 19:26:56This article was originally part of the sermon of Plebchain Radio Episode 111 (May 2, 2025) that nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpqtvqc82mv8cezhax5r34n4muc2c4pgjz8kaye2smj032nngg52clq7fgefr and I did with nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7ct4w35zumn0wd68yvfwvdhk6tcqyzx4h2fv3n9r6hrnjtcrjw43t0g0cmmrgvjmg525rc8hexkxc0kd2rhtk62 and nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpq4wxtsrj7g2jugh70pfkzjln43vgn4p7655pgky9j9w9d75u465pqahkzd0 of the nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcqyqwfvwrccp4j2xsuuvkwg0y6a20637t6f4cc5zzjkx030dkztt7t5hydajn
Listen to the full episode here:
<<https://fountain.fm/episode/Ln9Ej0zCZ5dEwfo8w2Ho>>
Bitcoin has always been a narrative revolution disguised as code. White paper, cypherpunk lore, pizza‑day legends - every block is a paragraph in the world’s most relentless epic. But code alone rarely converts the skeptic; it’s the camp‑fire myth that slips past the prefrontal cortex and shakes hands with the limbic system. People don’t adopt protocols first - they fall in love with protagonists.
Early adopters heard the white‑paper hymn, but most folks need characters first: a pizza‑day dreamer; a mother in a small country, crushed by the cost of remittance; a Warsaw street vendor swapping złoty for sats. When their arcs land, the brain releases a neurochemical OP_RETURN which says, “I belong in this plot.” That’s the sly roundabout orange pill: conviction smuggled inside catharsis.
That’s why, from 22–25 May in Warsaw’s Kinoteka, the Bitcoin Film Fest is loading its reels with rebellion. Each documentary, drama, and animated rabbit‑hole is a stealth wallet, zipping conviction straight into the feels of anyone still clasped within the cold claw of fiat. You come for the plot, you leave checking block heights.
Here's the clip of the sermon from the episode:
nostr:nevent1qvzqqqqqqypzpwp69zm7fewjp0vkp306adnzt7249ytxhz7mq3w5yc629u6er9zsqqsy43fwz8es2wnn65rh0udc05tumdnx5xagvzd88ptncspmesdqhygcrvpf2
-
 @ 5144fe88:9587d5af
2025-05-23 17:01:37
@ 5144fe88:9587d5af
2025-05-23 17:01:37The recent anomalies in the financial market and the frequent occurrence of world trade wars and hot wars have caused the world's political and economic landscape to fluctuate violently. It always feels like the financial crisis is getting closer and closer.
This is a systematic analysis of the possibility of the current global financial crisis by Manus based on Ray Dalio's latest views, US and Japanese economic and financial data, Buffett's investment behavior, and historical financial crises.
Research shows that the current financial system has many preconditions for a crisis, especially debt levels, market valuations, and investor behavior, which show obvious crisis signals. The probability of a financial crisis in the short term (within 6-12 months) is 30%-40%,
in the medium term (within 1-2 years) is 50%-60%,
in the long term (within 2-3 years) is 60%-70%.
Japan's role as the world's largest holder of overseas assets and the largest creditor of the United States is particularly critical. The sharp appreciation of the yen may be a signal of the return of global safe-haven funds, which will become an important precursor to the outbreak of a financial crisis.
Potential conditions for triggering a financial crisis Conditions that have been met 1. High debt levels: The debt-to-GDP ratio of the United States and Japan has reached a record high. 2. Market overvaluation: The ratio of stock market to GDP hits a record high 3. Abnormal investor behavior: Buffett's cash holdings hit a record high, with net selling for 10 consecutive quarters 4. Monetary policy shift: Japan ends negative interest rates, and the Fed ends the rate hike cycle 5. Market concentration is too high: a few technology stocks dominate market performance
Potential trigger points 1. The Bank of Japan further tightens monetary policy, leading to a sharp appreciation of the yen and the return of overseas funds 2. The US debt crisis worsens, and the proportion of interest expenses continues to rise to unsustainable levels 3. The bursting of the technology bubble leads to a collapse in market confidence 4. The trade war further escalates, disrupting global supply chains and economic growth 5. Japan, as the largest creditor of the United States, reduces its holdings of US debt, causing US debt yields to soar
Analysis of the similarities and differences between the current economic environment and the historical financial crisis Debt level comparison Current debt situation • US government debt to GDP ratio: 124.0% (December 2024) • Japanese government debt to GDP ratio: 216.2% (December 2024), historical high 225.8% (March 2021) • US total debt: 36.21 trillion US dollars (May 2025) • Japanese debt/GDP ratio: more than 250%-263% (Japanese Prime Minister’s statement)
Before the 2008 financial crisis • US government debt to GDP ratio: about 64% (2007) • Japanese government debt to GDP ratio: about 175% (2007)
Before the Internet bubble in 2000 • US government debt to GDP ratio: about 55% (1999) • Japanese government debt to GDP ratio: about 130% (1999)
Key differences • The current US debt-to-GDP ratio is nearly twice that before the 2008 crisis • The current Japanese debt-to-GDP ratio is more than 1.2 times that before the 2008 crisis • Global debt levels are generally higher than historical pre-crisis levels • US interest payments are expected to devour 30% of fiscal revenue (Moody's warning)
Monetary policy and interest rate environment
Current situation • US 10-year Treasury yield: about 4.6% (May 2025) • Bank of Japan policy: end negative interest rates and start a rate hike cycle • Bank of Japan's holdings of government bonds: 52%, plans to reduce purchases to 3 trillion yen per month by January-March 2026 • Fed policy: end the rate hike cycle and prepare to cut interest rates
Before the 2008 financial crisis • US 10-year Treasury yield: about 4.5%-5% (2007) • Fed policy: continuous rate hikes from 2004 to 2006, and rate cuts began in 2007 • Bank of Japan policy: maintain ultra-low interest rates
Key differences • Current US interest rates are similar to those before the 2008 crisis, but debt levels are much higher than then • Japan is in the early stages of ending its loose monetary policy, unlike before historical crises • The size of global central bank balance sheets is far greater than at any time in history
Market valuations and investor behavior Current situation • The ratio of stock market value to the size of the US economy: a record high • Buffett's cash holdings: $347 billion (28% of assets), a record high • Market concentration: US stock growth mainly relies on a few technology giants • Investor sentiment: Technology stocks are enthusiastic, but institutional investors are beginning to be cautious
Before the 2008 financial crisis • Buffett's cash holdings: 25% of assets (2005) • Market concentration: Financial and real estate-related stocks performed strongly • Investor sentiment: The real estate market was overheated and subprime products were widely popular
Before the 2000 Internet bubble • Buffett's cash holdings: increased from 1% to 13% (1998) • Market concentration: Internet stocks were extremely highly valued • Investor sentiment: Tech stocks are in a frenzy
Key differences • Buffett's current cash holdings exceed any pre-crisis level in history • Market valuation indicators have reached a record high, exceeding the levels before the 2000 bubble and the 2008 crisis • The current market concentration is higher than any period in history, and a few technology stocks dominate market performance
Safe-haven fund flows and international relations Current situation • The status of the yen: As a safe-haven currency, the appreciation of the yen may indicate a rise in global risk aversion • Trade relations: The United States has imposed tariffs on Japan, which is expected to reduce Japan's GDP growth by 0.3 percentage points in fiscal 2025 • International debt: Japan is one of the largest creditors of the United States
Before historical crises • Before the 2008 crisis: International capital flows to US real estate and financial products • Before the 2000 bubble: International capital flows to US technology stocks
Key differences • Current trade frictions have intensified and the trend of globalization has weakened • Japan's role as the world's largest holder of overseas assets has become more prominent • International debt dependence is higher than any period in history
-
 @ 04c915da:3dfbecc9
2025-05-16 18:06:46
@ 04c915da:3dfbecc9
2025-05-16 18:06:46Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Using stolen bitcoin for the reserve creates a perverse incentive. If governments see bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:59:23
@ 04c915da:3dfbecc9
2025-05-16 17:59:23Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:51:54
@ 04c915da:3dfbecc9
2025-05-16 17:51:54In much of the world, it is incredibly difficult to access U.S. dollars. Local currencies are often poorly managed and riddled with corruption. Billions of people demand a more reliable alternative. While the dollar has its own issues of corruption and mismanagement, it is widely regarded as superior to the fiat currencies it competes with globally. As a result, Tether has found massive success providing low cost, low friction access to dollars. Tether claims 400 million total users, is on track to add 200 million more this year, processes 8.1 million transactions daily, and facilitates $29 billion in daily transfers. Furthermore, their estimates suggest nearly 40% of users rely on it as a savings tool rather than just a transactional currency.
Tether’s rise has made the company a financial juggernaut. Last year alone, Tether raked in over $13 billion in profit, with a lean team of less than 100 employees. Their business model is elegantly simple: hold U.S. Treasuries and collect the interest. With over $113 billion in Treasuries, Tether has turned a straightforward concept into a profit machine.
Tether’s success has resulted in many competitors eager to claim a piece of the pie. This has triggered a massive venture capital grift cycle in USD tokens, with countless projects vying to dethrone Tether. Due to Tether’s entrenched network effect, these challengers face an uphill battle with little realistic chance of success. Most educated participants in the space likely recognize this reality but seem content to perpetuate the grift, hoping to cash out by dumping their equity positions on unsuspecting buyers before they realize the reality of the situation.
Historically, Tether’s greatest vulnerability has been U.S. government intervention. For over a decade, the company operated offshore with few allies in the U.S. establishment, making it a major target for regulatory action. That dynamic has shifted recently and Tether has seized the opportunity. By actively courting U.S. government support, Tether has fortified their position. This strategic move will likely cement their status as the dominant USD token for years to come.
While undeniably a great tool for the millions of users that rely on it, Tether is not without flaws. As a centralized, trusted third party, it holds the power to freeze or seize funds at its discretion. Corporate mismanagement or deliberate malpractice could also lead to massive losses at scale. In their goal of mitigating regulatory risk, Tether has deepened ties with law enforcement, mirroring some of the concerns of potential central bank digital currencies. In practice, Tether operates as a corporate CBDC alternative, collaborating with authorities to surveil and seize funds. The company proudly touts partnerships with leading surveillance firms and its own data reveals cooperation in over 1,000 law enforcement cases, with more than $2.5 billion in funds frozen.
The global demand for Tether is undeniable and the company’s profitability reflects its unrivaled success. Tether is owned and operated by bitcoiners and will likely continue to push forward strategic goals that help the movement as a whole. Recent efforts to mitigate the threat of U.S. government enforcement will likely solidify their network effect and stifle meaningful adoption of rival USD tokens or CBDCs. Yet, for all their achievements, Tether is simply a worse form of money than bitcoin. Tether requires trust in a centralized entity, while bitcoin can be saved or spent without permission. Furthermore, Tether is tied to the value of the US Dollar which is designed to lose purchasing power over time, while bitcoin, as a truly scarce asset, is designed to increase in purchasing power with adoption. As people awaken to the risks of Tether’s control, and the benefits bitcoin provides, bitcoin adoption will likely surpass it.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:12:05
@ 04c915da:3dfbecc9
2025-05-16 17:12:05One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 04c915da:3dfbecc9
2025-05-15 15:31:45
@ 04c915da:3dfbecc9
2025-05-15 15:31:45Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 08f96856:ffe59a09
2025-05-15 01:22:34
@ 08f96856:ffe59a09
2025-05-15 01:22:34เมื่อพูดถึง Bitcoin Standard หลายคนมักนึกถึงภาพโลกอนาคตที่ทุกคนใช้บิตคอยน์ซื้อกาแฟหรือของใช้ในชีวิตประจำวัน ภาพแบบนั้นดูเหมือนไกลตัวและเป็นไปไม่ได้ในความเป็นจริง หลายคนถึงกับพูดว่า “คงไม่ทันเห็นในช่วงชีวิตนี้หรอก” แต่ในมุมมองของผม Bitcoin Standard อาจไม่ได้เริ่มต้นจากการที่เราจ่ายบิตคอยน์โดยตรงในร้านค้า แต่อาจเริ่มจากบางสิ่งที่เงียบกว่า ลึกกว่า และเกิดขึ้นแล้วในขณะนี้ นั่นคือ การล่มสลายทีละน้อยของระบบเฟียตที่เราใช้กันอยู่
ระบบเงินที่อิงกับอำนาจรัฐกำลังเข้าสู่ช่วงขาลง รัฐบาลทั่วโลกกำลังจมอยู่ในภาระหนี้ระดับประวัติการณ์ แม้แต่ประเทศมหาอำนาจก็เริ่มแสดงสัญญาณของภาวะเสี่ยงผิดนัดชำระหนี้ อัตราเงินเฟ้อกลายเป็นปัญหาเรื้อรังที่ไม่มีท่าทีจะหายไป ธนาคารที่เคยโอนฟรีเริ่มกลับมาคิดค่าธรรมเนียม และประชาชนก็เริ่มรู้สึกถึงการเสื่อมศรัทธาในระบบการเงินดั้งเดิม แม้จะยังพูดกันไม่เต็มเสียงก็ตาม
ในขณะเดียวกัน บิตคอยน์เองก็กำลังพัฒนาแบบเงียบ ๆ เงียบ... แต่ไม่เคยหยุด โดยเฉพาะในระดับ Layer 2 ที่เริ่มแสดงศักยภาพอย่างจริงจัง Lightning Network เป็น Layer 2 ที่เปิดใช้งานมาได้ระยะเวลสหนึ่ง และยังคงมีบทบาทสำคัญที่สุดในระบบนิเวศของบิตคอยน์ มันทำให้การชำระเงินเร็วขึ้น มีต้นทุนต่ำ และไม่ต้องบันทึกทุกธุรกรรมลงบล็อกเชน เครือข่ายนี้กำลังขยายตัวทั้งในแง่ของโหนดและการใช้งานจริงทั่วโลก
ขณะเดียวกัน Layer 2 ทางเลือกอื่นอย่าง Ark Protocol ก็กำลังพัฒนาเพื่อตอบโจทย์ด้านความเป็นส่วนตัวและประสบการณ์ใช้งานที่ง่าย BitVM เปิดแนวทางใหม่ให้บิตคอยน์รองรับ smart contract ได้ในระดับ Turing-complete ซึ่งทำให้เกิดความเป็นไปได้ในกรณีใช้งานอีกมากมาย และเทคโนโลยีที่น่าสนใจอย่าง Taproot Assets, Cashu และ Fedimint ก็ทำให้การออกโทเคนหรือสกุลเงินที่อิงกับบิตคอยน์เป็นจริงได้บนโครงสร้างของบิตคอยน์เอง
เทคโนโลยีเหล่านี้ไม่ใช่การเติบโตแบบปาฏิหาริย์ แต่มันคืบหน้าอย่างต่อเนื่องและมั่นคง และนั่นคือเหตุผลที่มันจะ “อยู่รอด” ได้ในระยะยาว เมื่อฐานของความน่าเชื่อถือไม่ใช่บริษัท รัฐบาล หรือทุน แต่คือสิ่งที่ตรวจสอบได้และเปลี่ยนกฎไม่ได้
แน่นอนว่าบิตคอยน์ต้องแข่งขันกับ stable coin, เงินดิจิทัลของรัฐ และ cryptocurrency อื่น ๆ แต่สิ่งที่ทำให้มันเหนือกว่านั้นไม่ใช่ฟีเจอร์ หากแต่เป็นความทนทาน และความมั่นคงของกฎที่ไม่มีใครเปลี่ยนได้ ไม่มีทีมพัฒนา ไม่มีบริษัท ไม่มีประตูปิด หรือการยึดบัญชี มันยืนอยู่บนคณิตศาสตร์ พลังงาน และเวลา
หลายกรณีใช้งานที่เคยถูกทดลองในโลกคริปโตจะค่อย ๆ เคลื่อนเข้ามาสู่บิตคอยน์ เพราะโครงสร้างของมันแข็งแกร่งกว่า ไม่ต้องการทีมพัฒนาแกนกลาง ไม่ต้องพึ่งกลไกเสี่ยงต่อการผูกขาด และไม่ต้องการ “ความเชื่อใจ” จากใครเลย
Bitcoin Standard ที่ผมพูดถึงจึงไม่ใช่การเปลี่ยนแปลงแบบพลิกหน้ามือเป็นหลังมือ แต่คือการ “เปลี่ยนฐานของระบบ” ทีละชั้น ระบบการเงินใหม่ที่อิงอยู่กับบิตคอยน์กำลังเกิดขึ้นแล้ว มันไม่ใช่โลกที่ทุกคนถือเหรียญบิตคอยน์ แต่มันคือโลกที่คนใช้อาจไม่รู้ตัวด้วยซ้ำว่า “สิ่งที่เขาใช้นั้นอิงอยู่กับบิตคอยน์”
ผู้คนอาจใช้เงินดิจิทัลที่สร้างบน Layer 3 หรือ Layer 4 ผ่านแอป ผ่านแพลตฟอร์ม หรือผ่านสกุลเงินใหม่ที่ดูไม่ต่างจากเดิม แต่เบื้องหลังของระบบจะผูกไว้กับบิตคอยน์
และถ้ามองในเชิงพัฒนาการ บิตคอยน์ก็เหมือนกับอินเทอร์เน็ต ครั้งหนึ่งอินเทอร์เน็ตก็ถูกมองว่าเข้าใจยาก ต้องพิมพ์ http ต้องรู้จัก TCP/IP ต้องตั้ง proxy เอง แต่ปัจจุบันผู้คนใช้งานอินเทอร์เน็ตโดยไม่รู้ว่าเบื้องหลังมีอะไรเลย บิตคอยน์กำลังเดินตามเส้นทางเดียวกัน โปรโตคอลกำลังถอยออกจากสายตา และวันหนึ่งเราจะ “ใช้มัน” โดยไม่ต้องรู้ว่ามันคืออะไร
หากนับจากช่วงเริ่มต้นของอินเทอร์เน็ตในยุค 1990 จนกลายเป็นโครงสร้างหลักของโลกในสองทศวรรษ เส้นเวลาของบิตคอยน์ก็กำลังเดินตามรอยเท้าของอินเทอร์เน็ต และถ้าเราเชื่อว่าวัฏจักรของเทคโนโลยีมีจังหวะของมันเอง เราก็จะรู้ว่า Bitcoin Standard นั้นไม่ใช่เรื่องของอนาคตไกลโพ้น แต่มันเกิดขึ้นแล้ว
siamstr
-
 @ bf47c19e:c3d2573b
2025-05-24 18:17:09
@ bf47c19e:c3d2573b
2025-05-24 18:17:09Ovaj post sam objavio 24.01.2024. godine na Redditu povodom tri decenije od uvođenja Novog dinara kao rešenja za hiperinflaciju u Saveznoj Republici Jugoslaviji na šta su pojedini besni nokoineri sa te društvene mreže osuli drvlje i kamenje na mene. Od starih budalaština da je Bitkoin bezvredan, da nije oblik novca već finansijsko ulaganje, preko pravdanja svrhe inflacije, sve do potpune nemoći da se argumentima opovrgne nepobitna istina i pozivanja moderatora da me banuju. 🙃
Cena Bitkoina tada je bila oko $40.000. :)
Osim glavnog posta, ovde ću navesti i moje odgovore na neutemeljene i neinformisane tvrdnje besnih nokoinera. :) Da se sačuva od zaborava!
Juče se navršilo 30 godina "Deda Avramove reforme".
Dan kada je rođen novi dinar, a Deda Avram sasekao hiperinflaciju
Dva jajeta – nedeljna profesorska plata: Kako se živelo u hiperinflaciji i šta je uradio Avramović
Vikipedija: Jugoslovenski dinar
„U julu '93. godine u Jugoslaviji nisi mogao skoro ništa da kupiš i niko za dinare nije hteo ništa da prodaje“, pisao je Avramović. Centralno-bankarska prevara se nastavlja jer je već do kraja 1995. dinar oslabio prema marki za 70% (1 dinar = 3.4 DM), a u decembru 2000. je taj kurs već bio 30.5 dinara za 1 DM (-96.7% od uvođenja novog dinara). To samo pokazuje da redenominacija valute tj. "brisanje nula" nije nikako čudo i viđano je puno puta kroz istoriju)
Ako je reformom iz januara '94 god. 1 novi dinar vredeo kao 1 nemačka marka, zatim od 2002. uveden evro čime je realna vrednost marke (samim tim i dinara) prepolovljena, a danas 1 EUR vredi oko 117 RSD, to znači da je "deda Avramov dinar" prema evru već obezvređen 59.91 puta za 30 godina. Dakle devalvacija dinara od 5991% od 1994. godine, a svakako još veća izražena kroz dobra i usluge jer su i nemačka marka do 2002. i evro od svog uvođenja iste godine prošli kroz sopstvenu inflaciju. Sam evro je izgubio oko 38% vrednosti od 2002. godine. Tako da se može reći da i "deda Avramov dinar" već uveliko prolazi kroz hiperinflaciju koja je samo razvučena na mnogo duži vremenski period (ne brinite - znam "zvaničnu" definiciju hiperinflacije - još jedan "gaslighting" centralno-bankarskog kartela da zabašuri šta se iza brda valja). Jer šta je inflacija od preko 5991% nego višedecenijska hiperinflacija?! Kako ne shvata gigantske razmere ove prevare?!
ISPRAVKA: Dinar nije nominalno izgubio 23400% (234x) vrednosti prema nemačkoj marki/evru od 1994. godine, već 59.91x odnosno 5991%. I danas na sajtu NBS postoji zvanični srednji kurs marke prema dinaru od 59,91:1. Realno, obezvređivanje dinara i evra prema robama i uslugama je puno veće, pošto su cene roba i usluga izražene u evrima ubrzo udvostručene u periodu nakon uvođenja evra. Hvala članu DejanJwtq na ispravci i izvinjenje svima od mene zbog greške.
Dafiment i Jugoskandik ("Dafina i Jezda") su bili samo državna konstrukcija da se izvuku devize iz ruku naivnih investitora da bi te devize nešto kasnije poslužile kao tobožnja rezerva za novi dinar. Ova gigantska prevara je unapred bila planirana, a Deda Avram iskorišćen kao marioneta tadašnjeg režima.
Inače lista država koje su izvršile redenominaciju valute kroz "brisanje nula" je poprilično dugačka i radi se o uobičajenoj pojavi kroz istoriju još od Haitija 1813. godine, a poslednji put su to uradile Sijera Leone i Kolumbija 2021. godine. Odavno je zaboravljeno da je (SR) Jugoslavija devedesetih to učinila još 1990. (10.000:1), 1992. (10:1), 1993. (1.000.000:1) i 1994. pre Avramovića (1.000.000.000∶1) ali je ovaj dinar trajao samo 23 dana. Tako da Deda Avram nije izmislio toplu vodu.
U SFRJ je izvršena jedna redenominacija 1966. godine u odnosu 10.000:1.
Wikipedia: Redenomination
Kome i dalje nije jasno zašto Bitkoin neka više puta pažljivo pročita ove tekstove iznad: oblik novca koji se ne može redenominirati, veoma lako konfiskovati i izdavati bez ikakve kontrole i pokrića. Potpuno nezavistan od kaprica korumpiranih i od realnosti otuđenih političara i centralnih bankara. Veoma je bitno da postoji ovakav oblik novca koji nije podložan ovakvim manipulacijama od strane ljudskog faktora i da postoji slobodan izbor da se taj oblik novca odabere za štednju i transakcije: barem od strane onih koji ga razumeju, ovi koji ne žele da razumeju neka i dalje pristaju da budu pljačkani - njima ionako nema pomoći.
Komentari
brainzorz: Da, ali ako cemo realno bitkoin ne sluzi kao oblik novca, vec kao finansijsko ulaganje.
Bar je tako za nas i vecinu ljudi po svetu u praktičnom smislu. Jer 99.99% ljudi ili koliko vec prime platu u svojoj lokalnoj valuti, trose istu na redovan zivot, a ostatak (ako ga ima) investiraju. Slazem se da lokalne valute imaju svoj neki rizik, koji je veci u banana drzavi i da cuvanje svog kapitala u turbulentnom periodu u istoj je jako losa ideja.
Kada tako posmatras onda se mogu vuci pararele izmedju ostalih aseta, poput ETFova na primer i onda dolazimo do gomile problema sa bitkoinom.
@BTCSRB: Bitkoin se ne može porediti sa ETF-ovima pošto ETF-ove i ostale investicione instrumente ne možeš koristiti kao novac jer oni nisu "bearer assets" kao što jeste BTC. BTC eliminiše potpuno inflaciju (jer džabe ti keš u slamarici kao "bearer asset" kada je podložan inflaciji) i potrebu za posrednikom kod elektronskih plaćanja.
brainzorz: Ali on to eleminise samo u teoriji, sad da odem u pekaru, moram platiti u lokalnoj valuti, sad da li cu prodati bitkoin ili etf, prilicno je slicno.
Jedino sto mogu bitkoin zamenuti uzivo (ilegalno) sa nekim, pa tu jeste zamenjen posrednik. Ali provizije povlacenja su uglavnom zanemarljive, naspram ostalih parametara investicionog sredstva.
Neke stvari se mogu direktno platiti za bitkoin, ali to je ekstremno retko u stvarnom zivotu vecine ljudi.
@BTCSRB: Slažem se ali u uslovima hiperinflacije i visoke inflacije kakvu danas imamo u Argentini, Venecueli, Zimbabveu, Libanu, Turskoj itd. sve više ljudi direktno vrši transakcije u kriptovalutama, naročito "stablecoinima" poput USDT Tethera. Priznajem da u tim transakcijama BTC zaostaje upravo zbog volatilnosti ali je vršenje brzih i jeftinih transakcija svakako moguće putem Lightning mreže. Sve te lokalne valute su izgubile značajnu vrednost i prema USDT i prema BTC-u, odnosno BTC konstantno probija rekordnu vrednost kada se denominuje u tim valutama. I u tim državama je adopcija kriptovaluta najraširenija.
HunterVD: Kako valuta u koju se upumpavaju nepostojeci dolari i evri moze biti realna i dobra. A USDT tek da ne spominjem. Mozes uvek revi jer joj ljudi veruju, al ta vera u nesto ide samo do odredjenog nivoa.
@BTCSRB: Godinama kupujem BTC od svake plate, praktično štedim u njemu i kupovna moć mi vremenom raste denominirana u evrima i dinarima. To isto rade na desetine hiljada ljudi širom sveta. Kako su ti realni dinari i evri koje ubacujem svakog meseca koje sam zaradio od svog realnog rada - "nepostojeći"?
Kako dolari i evri koji se štampaju ni iz čega mogu biti realni i dobri kao valuta?
HunterVD: Pa eto bas to. Ulaze se nepostojeci novac u BTC i onda se prica o nekoj novoj valuti. Nije sija nego vrat, BTC ima jedino vrednost dok se upumpava taj lazni novac u njega. FIAT novac kolko tolko nastaje radom i proizvodnjom dobara, ne sav FIAT novac al neki deo, dok se BTC zasniva skroz na upumpavanje tog istog FIAT novca i dobroj volji i zeljama da magicne brojke idu navise.
@BTCSRB: Itekako je moguće izraziti cenu svih ostalih dobara i usluga kroz BTC i postojanje i vrednost BTC-a uopšte ne zavisi od fiat novca. Štaviše, gotova sva dobra i usluge dugoročno postaju jeftiniji kada se mere kroz BTC. Sutra kada bi fiat novac nestao BTC bi i dalje imao vrednost, čak i veću nego danas.
https://www.pricedinbitcoin21.com/
HunterVD: Naravno da je moguce izraziti cene svakodnevnih proizvoda u BTCu. Cene svakodnevnih proizvoda je moguce izraziti u cemu god pozelis, evo npr broj radnih sati koji je potreban da se proizvede taj proizvod i onda se uporedi sa cenom radnih sati i cene na polici, mozes ga uracunavati i u dobrima , jedan iphone kosta tolko i tolko KG juneceg mesa..... nista cudno. Takodje cene proizvoda pokazuju pad u odnosu sa BTCom jer je BTC masivno porastao u poslednjih 5-6 godina. Sta ce biti kad BTC stagnira ili pada kako se u tom periodu odnose cene, a da BTC je store of value i namenjen je samo da se cuva izvinte molim vas moja greska. Ni druge kripto valute nisu nista bolje. Ljudi koji su zaradili na BTCu svaka cast eto imali su pameti i srece , al sad kako je cena sve veca, inflacija sve losija i kamatne stope sve vise postace sve teze i teze dolaziti do novca a kamo li intvestirati ga u nesto rizicno ko kripto valute tako da ce i BTC sve manje rasti sto zbog velicine market cap-a sto zbog toga sto ljudi i firme imaju sve manje novca za ulagati. Dal ce btc moci da se uzbori sa inflacijom i losim uslovima to tek treba da se vidi. Tako da videcemo u narednom periodu koliko ce se ta priva o BTC kao store of value i nacinu odbrane od inflacije obistiniti. Licno ne verujem da ce BTC ikad biti zvanicno sredstvo placanja.
@BTCSRB: Cena svega se može izraziti kroz sve ostalo ali šta od svega toga najbolje vrši funkciju novca? BTC bolje vrši funkciju novca u većini okolnosti od gotovo svih stvari.
Šta će biti sa BTC videće se i oni koji veruju u njega će biti najzaslužniji za njegov uspeh jer su obezbeđivali potražnju kada su kola išla nizbrdo i za to biti asimetrično nagrađeni, ali će i puno izgubiti ako se pokaže da nisu u pravu. Pukovnici ili pokojnici. Po meni je to cilj zbog koga vredi rizikovati, pa i bankrotirati a cilj je da se centralno-bankarski kartel učini manje relevantnim.
Znaš i sam da fiat sistem ne može da preživi i izbegne imploziju bez konstantnog uvećanja mase novca u opticaju i zato se uopšte ne plašim za BTC i spavam mirno. BTC sigurno neće rasti istom brzinom kao prvih 15 godina ali moje očekivanje je svakako ubedljivo nadmašivanje svetske inflacije i obezvređivanja. Ne vidim kako sistem može da opstane bez novog QE kada god se on desi, u suprotnom imamo deflatornu spiralu.
Ne mora da bude zvanično sredstvo plaćanja, dovoljno da meni kao pojedincu služi za to dok god ima ljudi koji ga prihvataju, a ima ih puno. I da niko u tome ne može da nas spreči.
loldurrr: Ali i BTC je postao, u neku ruku, berzanska roba. Imaš market cap izražen u dolarima, koji je danas, npr. 2 triliona $, za mjesec dana 500 milijardi. Isto kao i dolar, samo volatilnije. Zato i kažem, da je to sve rezultat ponude i tražnje. Hipotetički, ja da imam milion BTC i odlučim to danas prodati, enormno ću oboriti cenu BTC. Ako je to valuta nezavisna od vanjskih uticaja - zašto će pasti toliko, kada imamo ograničenu količinu BTC-a. Svima je i dalje u podsvesti vrednost BTC izražena u USD, tako da je to isto kao i dinar, franak, akcija CocaCola i sl. Bar za sada...
A mogućnosti za korištenje BTC za robna plaćanja su mizerna. Ima li na vidiku mogućnosti da se vrednost nafte počne izražavati u BTC?
@BTCSRB: Meriti Bitkoin direktno prema robama i uslugama je itekako moguće i kada ga tako meriš, a ne prema fiat novcu, dugoročno cene gotovo svih roba i usluga padaju prema Bitkoinu. Cene svega izražene kroz BTC neće nestati ni u slučaju nestanka fiat novca, dolar sutra da prestane da postoji nikoga ne sprečava da izražava cene svega kroz BTC. Dolar i ostale valute nisu potrebni Bitkoinu.
Unlikely-Put-5524: Imam samo jedno pitanje za one "koji vide iza svega" i pronikli su bankarsku prevare da porobi čovečanstvo... Kako ne postoji mogućnost da je BTC i kripto nastao iz iste kuhinje i predstavlja ultimativni način za porobljavanje?
2% novčanika poseduje 95% svog BTC-a koji nije izgubljen. Znači da centralizacija može biti maksimalna...
@BTCSRB: Količina BTC-a u posedu ne daje kontrolu nad pravilima protokola i većinski vlasnici ne mogu da štampaju nove novčiće i tako uvećaju konačnu količinu u opticaju. Mogu samo da kratkoročno obore cenu i tako samo ostanu sa manje BTC-a koji imaju pošto će tržište vremenom apsorbovati te dampovane koine.
Unlikely-Put-5524: A mogu i dugoročno da obore cenu. Hajde da kažemo da imaš sada 10 BTC-a gde svaki vredi 40k
Veliki dumpu-ju ceo svoj bag u kontinutitetu kao što sad radi GS i posle godinu dana tvoj BTC sad vredi 4k, zašto misliš da bi ljudi nastavili da ga drže? Posebno ako znamo da ga 97% kupuje da bi zaradili, a ne zato što žele da ga koriste kao sredstvo plaćanja.
Ja bih ore BTC gledao kao commodity, jer sa svojim deflatornim svojstvima ne može biti valuta za plaćanje.
Takođe postoji i doomsday scenario gde jednostavno mogu svi da se dogovore da je ilegalan i to je onda to. Ovo mi deluje kao gotovo neverovatno, ali po meni je bilo koji maksimalizam potpuno detinjasto razmišljanje.
@BTCSRB: Pa padao je toliko puta za preko 70% i uvek se vraćao jer si uvek imao ljude koji su bili spremni da ga kupuju po bilo kojoj ceni, uključujući i mene. Pošto se ne može štampati, na kraju će ovi prodavci ostati bez BTC-a za prodaju i tržište apsorbovati čak i njihov "sell pressure". A ovi veliki koji drže tolike količine itekako dobro znaju vrednost toga što poseduju i nema smisla da svu količinu koju drže prodaju za inflatorni novac - prodavaće da bi finansirali svoj životni stil ili investiraju u biznise ili će ga koristiti kao kolateral za fiat pozajmice - ako raspolažu tolikim količinama i mogu da kontrolišu tržište nemaju strah da će im kolateral biti likvidiran.
Većina ljudi su fiat maksimalisti samim tim što su 100% u fiat novcu pa ne razmišljaju u pravcu doomsday scenarija kakav je upravo bila hiperinflacija devedesetih.
Romeo_y_Cohiba: Niko ti ne brani da ulažeš u bitcoin pod uslovom da znaš da je rizičniji od gotovog novca, štednje po viđenju, oročene štednje, obveznica, nekretnina, akcija, raznoraznih etfova, private equitya i derivata.
Drugim rečima ako ti je ok da danas uložiš 1000e, da za nedelju dana to vredi 500e, za mesec 1500 a za pola godina 300e ili 0 samo napred. Većini ljudi to nije ok.
Razlog zašto pamtimo Avrama je jer njegov dinar i dan danas koristimo. Prethodne uzastopne reforme nisu uspele kao što si i sam primetio.
Takođe, nije u pitanju "centralno-bankarska" prevara jer se ništa od toga ne bi desilo da ovom "odozgo" nisu zatrebale pare za finansiranje izvesnih stvari.
I dan danas, izvesni političar(i) izađu na TV i kažu da su "našli" novac za neki svoj genijalni plan i ljudi to puše. To u prevodu najčešće znači da će da nagna centralnu banku da mu doštampa novca i to nema veze sa bankama nego politikom..
@BTCSRB: Za investicione instrumente koje si naveo treba videti koliko su uspešno nadvladavali inflaciju prethodnih decenija i da li su očuvali kupovnu moć. Za štednju u banci i obveznice se i iz daleka vidi da nisu. US obveznice su u septembru imale drawdown od 48% od ATH iz 2020, a kao važe sa sigurnu investiciju. Čak i u momentu dospeća posle 10-30 godina jako teško čuvaju vrednost od inflacije.
A sada se zapitaj: da li zaista misliš da političari kontrolišu banke i bankare ili je možda obrnuto? Nisu političari ti koji su vlasnici krupnog kapitala.
Romeo_y_Cohiba: Ne investiraju svi na 10-30 godina za potrebe penzije. To je samo jedan od mnogo vidova i razloga investiranja. Nadvladavanje inflacije je isto tako samo jedan od kriterijuma. Samo pogledaš u šta jedan penzioni fond u SAD-u investira(hint: nije btc i nisu samo akcije). Npr. neki penzioni fondovi su od skoro počeli da investiraju u private equity ali isključivo do 15% veličine portfolija. Počeće i sa kriptom u nekom trenutku ali mogu da potpišem da će biti u još manjem procentu nego PE. Niko nije blesav da grune teško stečeni novac u nešto tako rizično osim u jako malim iznosima.
Ne znam ko koga kontroliše ali Avram je bio daleko manji baja od Slobe 90ih i pitao se za stvari samo u meri koliko mu je bio dozvoljeno da se pita. Ratovanje košta i finansira se štampanjem novca, nisu to neke neshvatljive stvari. Da ne pričam da smo bili pod apsolutnim sankcijama celog sveta.
Virtual_Plenty_6047: Npr jedan od velikih uspeha Japana od pre par decenija je zahvaljujući devalvaciji njihove valute, pa samim tim izvoz im je bio relativno jeftin. Naš dinar je jak, i to odgovara uvozničkom lobiju.
Nažalost mi ionako ništa ne proizvodimo tako da ne verujem da bi nešto pomoglo ako bi devalvirali dinar. Al svakako ovo je jedna viša ekonomija za koju naši političari nisu dorasli.
@BTCSRB: Gde je običan čovek u tom velikom japanskom uspehu? Postali su zemlja starih i nesrećnih mladih ljudi koji ne mogu da pobegnu iz "hamster wheel-a". Imaju "debt to GDP" od preko 260%. Taj dug nikada neće vratiti, a uz to će povući u ambis pola sveta jer najveći držaoci američkog duga - 14.5%. Spolja gladac, iznutra jadac. Iako je malo degutantno da mi iz Srbije komentarišemo Japance, opet pitam: gde je prosečan Japanac u celoj ovoj igri?
Why Japan Is Facing a Financial Disaster
Preporučujem da pogledate dokumentarac "Princes of the Yen | The Hidden Power of Central Banks" snimljenom po istoimenoj knjizi profesora Riharda Vernera koji je otac kvantitativnog popuštanja (quantitative easing) i ekspert za japansku ekonomiju i bankarski sistem.
Virtual_Plenty_6047: Zato sam rekao od pre nekoliko decenija. Jer su do pre nekih 30 godina bili 50 godina ispred celog sveta, sad su 20 godina iza naprednog sveta. Japanci su svako specifični. Poenta mog komentara da postoji razlog za neke zemlje da oslabe svoju valutu, i može itekako dobro da radi ako se radi u sinergiji sa nekim drugim ekonomskim merama. Tako da odgovor na to opet pitam, ne znam gde je prosečni Japanac, uskoro tamo trebam da idem pa ću ti reći. :'D
Odgledao sam ja ovaj dokumentarac odavno, super je. Pročitao mnoge knjige, a ponajviše od Austrijske ekonomske škole gde su pojedinci (Hayek) bili prvi koji su zagovarali novu decentralizovanu valutu, bili su u toj školi mnogi koji su prvi pričali o problemu inflacije i šta je tačno inflacija, ali su bili i za kapitalizam. Ali ovo je zaista jedna visoka ekonomija, videćeš da nije baš sve tako jednostavno kao što misliš.
Malo si previše u kriptovalutama pa gledaš na sve drugo u ekonomiji sa prekorom, pogotovu na kapitalizam. Evo i ja sam sam dobro investiran u kripto (uglavnom u BTC) pa sam itekako svestan da sve to može na kraju da bude potpuna pizdarija.
p.s. Knjiga za preporuku: 23 stvari koje vam ne kazu o kapitalizmu
@BTCSRB: Nisam u kriptovalutama nego isključivo u BTC.
Nisam ja protiv kapitalizma samo što nije pravi kapitalizam kada ne postoji slobodno tržište novca, pa samim tim ne postoji uopšte slobodno tržište koliko god se činilo tako. Kada su ekonomski subjekti prisiljeni da koriste određeni oblik novca, a monetarna politika se centralno planira - po meni tu nema slobodnog tržišta niti kapitalizma. Npr. formiranje cene Bitkoina i transakcionih naknada je čisto slobodno tržište jer tu nema "bailout-a", a BTC mining industrija je pravi primer slobodnog tržišta u kapitalizmu. Čista ponuda i potražnja bez intervencionizma. Ako si neprofitabilan nema ti spasa i bankrotiraćeš i nema nikoga ko će ti priteći u pomoć. Niko nije "too big to fail".
Znam da sam se ovde usredsredio usko na jednu industriju ali se može primeniti na celokupnu ekonomiju. Države i centralne banke su suvišne i apsolutno pokvare sve čega se dotaknu pa će u slučaju potpune pizdarije odgovornost biti na njima, a ne na Bitkoinu i njegovim držaocima.
kutija_keksa: Evo zašto btc nije pogodan kao valuta:
-Volatilna vrednost. Vrednost btc se menja i do 200% godišnje, dok dolar ne trpi inflaciju vecu od 10% godišnje (mada je u redovnim uslovima tipa 3%). Čak i dinar, ako gledaš realnu kupovnu moć u prodavnici nema volatilnost preko 30% na godišnjem nivou (jedno 7 puta nižu od BTC) Ako danas kupim BTC u vrednosti od 15 USD ne znam da li ću sutra moći da kupim 10 ili 20 USD za isti taj BTC.
-„Gas fees” koji se plaćaju na svaku transakciju, u poređenjusa kešom koji nema takvih problema.
-Spor transfer novca. Arhitektura blockchaina ne dozvoljava mreži da procesuira više od 10 transakcija po sekundi, što značida na transakciju možete čekati i po nekoloo sati, u poređenju sa kešom (bez odugovlačenja) ili debitnim karticama (10 sekundi do 10 minuta). Visa i MasterCard procesuiraju hiljadu puta više transakcija po sekundi.
-Retko ko eksplicitno prima BTC, tako da ćete plaćati menjačnici na kursu u oba smera, i pritom čekati menjačnicu.
-Podložan je manipulacijama velikih igrača poput Ilona Maska i velikih banki koje su u zadnjih pet godina debelo uložile u kripto. Fiat je na milosti države i njenih građana, dok je BTC na milost privatnih investitora. Kome verujete više?
-SVE BTC transakcije su jsvne, ako neko zna koji novčanik je vaš lako zna i koliko para ste kada slali kome, dok fizičke novčanice nemaju taj problem.
-Vrednost i upotreljivost BTC ne garantuje niko, dok vrednost i upotrebljivost fiat valute barem donekle garantuje država. Na primer, Srbija garantuje da je dinar upotrebljiv jer zahteva da vodu, struju, poreze, namete i takse plaćaš u dinarima, a i javni sektor (10% čitavog stanovništva) isplaćuje isključivo u dinarima.
OP očigledno ima jako ostrašćenu ideološku perspektivu... Ja nisam stručnjak, ali je moj otac pisao naučne radove o blockchainu dok je bio na doktorskim studijama, još kad je pomisao o BTC vrednijem od sto dolada bila smešna, tako da znam nešto malo kroz priče sa njim. Uostalom, sve o čemu pričam lako je proveriti pomoću javnih podataka. Ono što OP piše je jednim delom tačno, ali su iznete samo one informacije koje idu u prilog BTC.
Kripto kao pobuna protiv fiata, centralnih banaka i vlada je imao ideološke korene kod anarhista na internetu devedestih, međutim od njihovih belih papira i špekulacija dobili smo nešto što je kao valuta beskorisno. BTC može biti investicija, ako su ljudi iskreni sa sobom, ali ideja o valuti je prevaziđena. Ako i neka kripto valuta drži do toga onda je to Monero koji bar ima anonimnost.
@BTCSRB: Ne ulazeći u sve iznete navode taksativno, ipak moram da prokomentarišem neke od nepreciznih ili netačnih navoda.
Transakcione naknade kod Bitkoina se ne zovu "gas fees" već "transaction fees". Kod keša nema takvih problema ali ga ne možete poslati putem komunikacionog kanala bez posrednika. To mora da ima svoju cenu pošto BTC majneri moraju da imaju neki podsticaj da uključe nečiju transakciju u blok koji je ograničene veličine. BTC "fee market" je najslobodnije tržište na svetu. Fiat novac nemate mogućnost da pošaljete na daljinu bez posrednika koji takođe naplaćuje nekada dosta skupe naknade.
Besmisleno je porediti blokčejn kao "settlement layer" sa Visom i Mastercardom koje ne služe za finalno poravnanje. Glavni Bitkoin blokčejn se može pre uporediti s SWIFT-om ili FedWire-om kod kojih je jednom poravnata transakcija nepovratna, a Mastercard/Visa sa BTC "Lightning Network-om" koji služi za brza i jeftina plaćanja. Otac je trebalo da Vas nauči o Lightning mreži, kako funkcioniše i da je sposobna da procesuira više miliona transakcija u sekundi. Lightning mreža takođe nudi veći nivo privatnosti od glavnog blokčejna ali puno manju sigurnost.
Ne bih se složio da je fiat na milosti isključivo države i građana, samo ću spomenuti Crnu sredu iz septembra 1992. godine i spekulativni napad na britansku funtu.
BTC transakcije su javne ali su pseudonimne što znači da je jako teško utvrditi identitet ukoliko adresa nije povezana sa identitetom korisnika. Generisanje BTC adrese ne zahteva nikakvu identifikaciju ("krvnu sliku") za razliku od otvaranja bankovnog računa. Može se generisati neograničen broj adresa i na razne načine prekinuti i zamaskirati veza transakcija između njih radi očuvanja privatnosti. Ponovo, fizičke novčanice ne možemo slati putem komunikacionog kanala bez posrednika, podložne su konfiskaciji, uništenju i obezvređivanju.
Upotrebljivost Bitkoina garantuje "open source" kod, energija, matematika i kriptografija. To su mnogo jače garancije nego obećanja bilo koje države koja su toliko puta u istoriji izigrale poverenje sopstvenog stanovništva - poput Jugoslavije devedesetih.
Ja sam BTC spomenuo kao potencijalno rešenje za (hiper)inflaciju tek u kraćem delu na kraju teksta, a od Vas i od ostalih komentatora sam dobio nesrazmeran odgovor usmeren na Bitkoin, a puno manje usmeren na navode iz najvećeg dela posta.
Tako ste i vi izneli isključivo informacije koje ne idu u prilog BTC-a, a potpuno ignorisali sve očigledne nedostatke fiat novca (kako u fizičkom, tako i u digitalnom obliku) koji su se i ispoljili tokom hiperinflacije devedesetih, a ispoljavaju se i dan-danas.
Svako dobro!
kutija_keksa: Zato su i „Gas fees” pod navodnicima.
Ne vidim zašto bi bilo dobro imati „slobodno tržište” kada se radi o kopačima.
Ali, čak i da je dobro imati slobodno tržište, morate primetiti da BTC kopanje nije tako slobodno. Postojanje ASIC mašina znači da se kopanje prevashodno isplati velikim igračima (ne mislim na likove sa 3 riser kartice u PC, nego na kineze sa skladištima teških preko milion u opremi). Takođe, te velike operacije organi vlasti mogu zaustaviti kad im se prohte (Kina).
Jako je teško izvući BTC anonimno bez gubitka kod menjača -- pojedinca ili non KYC institucije.
Što se upotrebljivosti BTC tiče, šta meni garantuje da ću imati na šta da potrošim BTC? To je ključno pitanje. A kasa Jugoslovenski fiat nije bio upotebljiv, vidim da Nemački jeste. Isto tako, mislim da će USD biti upotrebljiv dugo, a kada USD bude neupotrebljiv društvo će ionako biti u apokalipsi gde papir nije važan koliko i hrana, utočište, voda, radio, municija, lekovi i vatreno oružje.
Naravno da iznosim samo informacije koje proizilaze iz nedostataka, to je balans postu i komentarima. Da su ljudi samo blatili kripto moj komentar bi mnogo više ličio na originalni post nego na moj prošli komentar. Ja se sa mnogim tvrdnjama u postu slažem delimično ili potpuno, samo želim da pružim kontekst za tumačenje toga.
Ideološki su mi Cryptopunks potpuno zanimljivi, ali cinizam je opravdan kada se u obzir uzme priča. Ljudi su želeli da se odupru bankama, vladama, kontroli i prismotri. Izmislili su tehnologiju. Počeli su da koriste i popularizuju tu tehnologiju. U prostor su ušle banke i vlade, kupovanjem, prodajom i praćenjem samog tržišta (danas sve velike menjačnice imaju KYC procedure). Kao u matriksu, kontrolisana opozicija. Ok, ovo je lična teorija zavere u koju ni ja ne verujem u potpunosti.
Ako govorimo o crypto kao valuti mislim da je XMR mnogo bolja VALUTA od BTC, dok je mnogo gora investicija. Jednostavno se slažem sa političkim i ideološkim ciljevima pionira kripto valuta, ali smatram da su oni ogromnim delom iznevereni zbog ulaska banaka i država u celu priču, te njihova stara rešenja više ne rešavaju originalne probleme.
@BTCSRB: BTC kao neutralni novac je za svakoga, pa i za bankare i države. Ne možemo ih sprečiti da ga kupe na tržištu i stave ga u kakav god instrument, pa i ETF. Ne možemo ih sprečiti da ga konfiskuju od onih koji nisu dobro obezbedili svoje ključeve. Države su regulisale ono što su mogle, poput menjačnica, kroz AML/KYC procedure ali kakve to veze ima sa BTC-om? Na protokol kao protokol nisu mogle da utiču.
Ko želi i dalje može koristiti BTC kako je i prvobitno predviđeno - za p2p transakcije i skladištenje vrednosti u "self custody-u". Bitkoin je i dalje "bearer asset" otporan na cenzuru i konfiskaciju. Ne vidim da je taj pravac promenjen samo zato što su ušle banke i države. Možda nije u duhu Bitkoina da ga kupuju fondovi pa ga prodaju upakovanog u ETF. Najmanje je u duhu bitkoina da se nekome zabrani da ga kupuje.
Kako to mislite "ne vidite zašto bi bilo dobro imati „slobodno tržište” kada se radi o kopačima? Na decentralizaciji mininga se radi (StratumV2 protkol, Ocean pool...), a kineski primer je samo pokazatelj koliko je otporno: nakon zabrane raširilo se dodatno po svetu, a u Kini se i dalje nalazi 21% hešrejta. Majneri imaju veoma male margine profita zbog same prirode rudarenja i halvinga pa će bilo kakav "fck around" poput cenzure transakcija verovatno značiti bankrot.
Možemo do sutra pričati o XMR vs BTC i navešću puno razloga zašto XMR ne može i neće zaživeti kao novac, a pre svega je manjak decentralizacije (neograničena veličina blokčejna) i otpornost na državni napad - sve što Bitkoin ima. Kada je novac u pitanju pobednik nosi sve i tu je Monero već izgubio, dok će BTC poboljšanu privatnost obezbediti na ostalim nivoima, sidechainovima itd (Lightning, Liquid, Cashu, Fedimint, Ark i ko zna šta sve što još i ne postoji - nivo developmenta u Bitkoin prostoru je ogroman).
Dolar će uvek u nekom obliku biti upotrebljiv ali ne znači da će zauvek ostati svetska rezervna valuta, kao što i danas postoji funta ali odavno nije više ono što je bila na vrhuncu Britanske imperije.
kutija_keksa: Pa ti protokoli sprečavaju pljude da anonimno kupe BTC.
Mislim, BTC realno ima neku primenu, ali ja ga danas npr. imam čisto kao neku malu investicijicu, i to još od doba kad je kopanje sa 2 grafičke u kućnom PC bilo isplativo po skupoj struji. Ali BTC prosto nije dobra alternativa fizičkom novcu na nivou države zbog volatilnosti i manjka kontrole. Jedna ogromna poluga države je puštanje u promet novog novca, i tako se kontroliše inflacija, pored menjanja kamatnih stopa. Bez mogućnosti štampe gubi se i taj faktor kontrole. A inflacija od 2-3% godišnje je zdrava, dok je za ekonomiju deflacija (kojoj je BTC bar delimično sklon) haos, jer smanjuje ekonomsku aktivnost i investicije...
Što se tiče državnog napada na XMR, misliš na to kako jedna država može da realistično sprovede 51% napad?
XMR nije vrhovna valuta ali meni se sviđa kako za njega nema ASIC mašina, kako je anoniman u smislu da ne možeš lako da provališ ko kome koliko i kada šalje šta... Mislim da će XMR sigurno u toj privacy niši zameniti neka druga valuta kroz 10-15 godina koja ima bolji algoritam i tehnologiju...
Dobra dosetka za veličinu blockchaina, ali ona je trenutno 160GB cela / 50 GB pruned, tako nešto. Sve dok nije preko 10TB (100x) veća može je pohraniti najveći hard disk namenjen „običnim ljudima”, a kad se dođe do tad verovatno će i cene tih diskova biti pristupačnije nego danas. Sa druge strane, agresivan pruning je takođe opcija. A da ne govorimo o sidechainovima koji takođe postoje za XMR.
Da, to za dolar je i moja poenta, nekako će biti upotrebljiv uvek, dok je kripto neupotrebljiv bez neta, a i nema mnogo šta da se kupi kriptom u poređenju sa fiatom. I
@BTCSRB: Ima bezbroj načina da se nabavi non-KYC Bitkoin: coinjoin, coinmixing, rudarenje u non-KYC pulu, nabavka nekog drugog kripta putem KYC menjačnice pa "trustless atomic swap" za BTC, nabavka KYC BTC-a putem Lightning-a pa "submarine swap" on-chain, zatim nabavka bilo kog KYC kripta ili Lightning ili on-chain BTC-a pa swap na sidechain Liquid BTC gde su transakcije tajne slično XMR-u i nazad swap na on-chain. Naravno i stara narodska razmena na ulici. XMR se isto može koristiti za svrhu nabavke non-KYC Bitkoina. U svim ovim slučajevima se adrese koje su krajnje destinacije tih sredstava ne mogu ili jako teško povezati sa KYC identitetom korisnika. Više na: kycnot.me
Diskusija o tome da li je zdrava i potrebna inflacija i da li je uopšte potreban državni intervencionizam u ekonomiji je stara diskusija između Kejnzijanske i Austrijske ekonomske škole. Po meni svaka inflacija je pljačka. Da ne govorimo da centralni bankari ne snose nikakvu odgovornost za gubitak kontrole nad inflacijom koji se meri u stotinama procenata "omaška" jer kada je ciljana inflacija 2%, a imamo inflaciju od 10% to je onda promašaj od 500%. A svi vodeći centralni bankari su i dalje na svojim funkcijama od početka inflacije negde 2020. godine iako su izneverili sva očekivanja. Nisu izabrani od strane naroda i nemoguće ih je smeniti od strane naroda, a utiču na živote svih!
Usled tehnološkog napretka i rasta produktivnosti, prirodno stanje slobodnog tržišta je pad cena, a ne njihov konstantan rast kroz inflaciju. Ne postoji nikakva "poželjna" ili "neophodna" inflacija, svaka "ciljana" inflacija je pljačka koji onemogućava populaciju da uživa u plodovima sopstvene produktivnosti u obliku nižih cena svih roba i usluga. Bitkoin zbog svoje fiksne ponude novca u opticaju (21 milion novčića = apsolutna digitalna oskudnost) nameće ovu disciplinu slobodnog tržišta i tehnološkog napretka. Dok je postojeći dužnički fiat sistem dizajniran da krade plodove produktivnosti, Bitkoin omogućava populaciji da ih zadrži u obliku nižih cena.
Kada nema rasta cena, inflacija je 0% i cene su stabilne. Krađa i tada postoji, jer cene prirodno padaju zbog povećanja efikasnosti proizvodnje/usluga, gde bi se tada veca količina robe/usluga, takmičila za istu (fiksnu) količinu novča od 21M BTC-a.
Kakav je ishod ove diskusije nije bitno, bitno je da sada svako ima slobodu izbora kakav novac želi da koristi a ne da bude prisiljen da koristi isključivo inflatorni novac. Ako se neko ne slaže sa modernom monetarnom teorijom, sada ima alternativu koju nekada nije imao (zlato je odavno izgubilo bitku sa MMT) pre postojanja Bitkoina.
kutija_keksa: Neki od ovih non kyc nacina su mi vec bili poznati, neki nisu, ovo je bas informativan komentar.
A što je inflacija pljačka? Bez obzira na inflaciju, broj novčanica u novčaniku ostaje isti, to što se one sada mogu zameniti za manje robe je druga priča. Da li je onda i zlato pljačka, jer neko kupi, na primer, 100g zlata danas, a sutra na tržištu cena zlata padne? Da li je onda pljačka i BTC, jer i danas i kad je BTC bio na vrhuncu cene imam isti broj satoshija, samo je danas njihova vrednost manja?
Ne vidim zašto bi centralni bankari snosili odgovornost zbog inflacije. Oni ugrobo imaju dve poluge za kontrolu inflacije: kamatne stope i štampanje novca. U realnosti na inflaciju utiče mnogo faktora na koje centralna banka nema uticaj, niti koje može da predvidi: pandemije, ratovi, državni budžeti i zaduživanja, trgovina u datoj valuti (i izvoz i uvoz), porast i pad produktivnosti... Oni imaju donekle uticaj, ali nisu svemoćni.
Što se tiče izbora, ovo već zalazi u politiku a ne u finansije, ali ni direktor pošte, ni direktor EPS, ni direktor vodovoda nisu birani na izborima na kojima glasaju svi, a utiču na živote svih!
Ne verujem u kripto kao spasioce kapitalizma ili pojedinca. Ovo je sada više politički, ali zaista mislim da u kapitalizmu prosečna osoba nema slobode, a da je kripto u najbolju ruku jedna mala stavka koja omogućava skladištenje stečenog kapitala (ovo se dobija ako prihvatimo sve kripto pozitivne teze), ali ne rešava problem radnika koji čine 95% društva i doprinose 99% vrednosti a kapitala kontrolišu višestruko manje.
Otkud znam, ono, da rezimiram: kripto je koristan alat koji još nije dostigao svoj vrhunac, ali neće nešto mnogo promeniti svet. To je neko moje viđenje.
@BTCSRB: Kako nije pljačka? Broj novčanica u novčaniku ostaje isti ali ukupan broj novca u opticaju se uvećava i tako obezvređuje tvoje novčanice. Inače, znaš vrlo dobro da fizički keš čini manje od 10% ukupnog novca u opticaju, a ostalo je digitalno. Dakle "money supply" se uvećava pritiskom na dugme tastature računara u FED/ECB/NBS... Neko stvara novac ni iz čega za koji svi moramo da radimo trošeći svoje dragoceno i ograničeno vreme na ovom svetu. Tako nam efektivno krade vreme pošto tvoj radni sat iz prošlosti konstantno može da kupi manje roba i usluga u budućnosti, a zbog tehnološkog napretka i rasta produktivnosti bi realno cene trebaju da budu niže vremenom
Kako možeš da porediš fiat, zlato i BTC u tom smislu? Vrednost fiata prevashodno smanjuje ljudska manipulacija sa strane ponude koja se uvek uvećava, dok je potražnja permanentno rastuća zbog zakona o "legal tenderu" i rasta privrede i broja stanovnika. Ovo sa BTC je strana potražnje koju reguliše slobodno tržište dok ukupna ponuda nije podložna ljudskoj manipulaciji. Dugoročno, vrednost zlata i BTC raste sa rastućom potražnjom jer nema manipulacije ponude.
Centralni bankari će optužiti sve druge faktore da bi skrenuli pažnju sa svoje odgovornosti za inflaciju, a za ratove se može reći da su čak i saučesnici pošto tokovi novca mogu utvrditi veoma zanimljivu vezu između njih i vojno-industrijskog kompleksa. Na stranu to, dolarska monetarna masa je samo između februara i aprila 2020. uvećana za 1.39 biliona/triliona što je više nego ukupna monetarna masa iz 2008-09 krize. U krizi 2008-09 su od septembra 2008. do januara 2009. naštampali 803 milijarde i tako uvećali monetarnu masu za 88% sa 909 milijardi na 1712 milijardi - to znači da su 4 meseca naštampali skoro isto novca kao tokom celih 95 prethodnig godina sopstvenog postojanja Federalnih rezervi. Te 2020. su i potpuno ukinuli obavezne rezerve u komercijalnim bankama.
ECB je naštampala 1T evra "zbog kovida". A kao naštampali su jer je bila zatvorena celokupna privreda, pa što ste tako agresivno zatvarali privredu - trebalo je da pustite ljude da rade a ne da se igrate Mao Ce Tunga. I uprkos nezapamćenom štampanju ti isti centralni bankari su nazivali inflaciju "prolaznom" - dakle ni zrnce odgovornosti.
Ako u kapitalizmu prosečna osoba nema slobode, šta reći za komunizam gde ne da nema slobode nego nema ni života pošto su komunistički režimi pobili na desetine miliona ljudi?
Na hipotetičkom BTC standardu zbog fiksne količine novca u opticaju bi se popravio položaj radnika jer kapitalisti ne mogu da beskonačno uvećavaju svoj BTC kapital i kupovna moć i radnika i kapitalista bi procentualno podjednako rasla i običan radnik bi imao mnogo bolje šanse da i sam postane kapitalista nego danas. Imao bi mogućnost da štedi od svoje plate jer mu novac ne bi gubio vrednost i u nekom trenutku bi iz svoje štednje finansirao neki biznis, a ne zaduživanjem. Tako bi se ravnomernije rasporedilo društveno bogatstvo ali ne centralnim planiranjem nego kroz slobodno tržište.
-
 @ 3283ef81:0a531a33
2025-05-24 18:12:47
@ 3283ef81:0a531a33
2025-05-24 18:12:47Lorem ipsum dolor sit amet, consectetur adipiscing elit\ enean magna lorem, dignissim et nisl a, iaculis eleifend dolor
uspendisse potenti
-
 @ 7460b7fd:4fc4e74b
2025-05-21 02:35:36
@ 7460b7fd:4fc4e74b
2025-05-21 02:35:36如果比特币发明了真正的钱,那么 Crypto 是什么?
引言
比特币诞生之初就以“数字黄金”姿态示人,被支持者誉为人类历史上第一次发明了真正意义上的钱——一种不依赖国家信用、总量恒定且不可篡改的硬通货。然而十多年过去,比特币之后蓬勃而起的加密世界(Crypto)已经远超“货币”范畴:从智能合约平台到去中心组织,从去央行的稳定币到戏谑荒诞的迷因币,Crypto 演化出一个丰富而混沌的新生态。这不禁引发一个根本性的追问:如果说比特币解决了“真金白银”的问题,那么 Crypto 又完成了什么发明?
 Crypto 与政治的碰撞:随着Crypto版图扩张,全球政治势力也被裹挟进这场金融变革洪流(示意图)。比特币的出现重塑了货币信用,但Crypto所引发的却是一场更深刻的政治与治理结构实验。从华尔街到华盛顿,从散户论坛到主权国家,越来越多人意识到:Crypto不只是技术或金融现象,而是一种全新的政治表达结构正在萌芽。正如有激进论者所断言的:“比特币发明了真正的钱,而Crypto则在发明新的政治。”价格K线与流动性曲线,或许正成为这个时代社群意志和社会价值观的新型投射。
Crypto 与政治的碰撞:随着Crypto版图扩张,全球政治势力也被裹挟进这场金融变革洪流(示意图)。比特币的出现重塑了货币信用,但Crypto所引发的却是一场更深刻的政治与治理结构实验。从华尔街到华盛顿,从散户论坛到主权国家,越来越多人意识到:Crypto不只是技术或金融现象,而是一种全新的政治表达结构正在萌芽。正如有激进论者所断言的:“比特币发明了真正的钱,而Crypto则在发明新的政治。”价格K线与流动性曲线,或许正成为这个时代社群意志和社会价值观的新型投射。冲突结构:当价格挑战选票
传统政治中,选票是人民意志的载体,一人一票勾勒出民主治理的正统路径。而在链上的加密世界里,骤升骤降的价格曲线和真金白银的买卖行为却扮演起了选票的角色:资金流向成了民意走向,市场多空成为立场表决。价格行为取代选票,这听来匪夷所思,却已在Crypto社群中成为日常现实。每一次代币的抛售与追高,都是社区对项目决策的即时“投票”;每一根K线的涨跌,都折射出社区意志的赞同或抗议。市场行为本身承担了决策权与象征权——价格即政治,正在链上蔓延。
这一新生政治形式与旧世界的民主机制形成了鲜明冲突。bitcoin.org中本聪在比特币白皮书中提出“一CPU一票”的工作量证明共识,用算力投票取代了人为决策bitcoin.org。而今,Crypto更进一步,用资本市场的涨跌来取代传统政治的选举。支持某项目?直接购入其代币推高市值;反对某提案?用脚投票抛售资产。相比漫长的选举周期和层层代议制,链上市场提供了近乎实时的“公投”机制。但这种机制也引发巨大争议:资本的投票天然偏向持币多者(富者)的意志,是否意味着加密政治更为金权而非民权?持币多寡成为影响力大小,仿佛选举演变成了“一币一票”,巨鲸富豪俨然掌握更多话语权。这种与民主平等原则的冲突,成为Crypto政治形式饱受质疑的核心张力之一。
尽管如此,我们已经目睹市场投票在Crypto世界塑造秩序的威力:2016年以太坊因DAO事件分叉时,社区以真金白银“投票”决定了哪条链获得未来。arkhamintelligence.com结果是新链以太坊(ETH)成为主流,其市值一度超过2,800亿美元,而坚持原则的以太经典(ETC)市值不足35亿美元,不及前者的八十分之一arkhamintelligence.com。市场选择清楚地昭示了社区的政治意志。同样地,在比特币扩容之争、各类硬分叉博弈中,无不是由投资者和矿工用资金与算力投票,胜者存续败者黯然。价格成为裁决纷争的最终选票,冲击着传统“选票决胜”的政治理念。Crypto的价格民主,与现代代议民主正面相撞,激起当代政治哲思中前所未有的冲突火花。
治理与分配
XRP对决SEC成为了加密世界“治理与分配”冲突的经典战例。2020年底,美国证券交易委员会(SEC)突然起诉Ripple公司,指控其发行的XRP代币属于未注册证券,消息一出直接引爆市场恐慌。XRP价格应声暴跌,一度跌去超过60%,最低触及0.21美元coindesk.com。曾经位居市值前三的XRP险些被打入谷底,监管的强硬姿态似乎要将这个项目彻底扼杀。
然而XRP社区没有选择沉默。 大批长期持有者组成了自称“XRP军团”(XRP Army)的草根力量,在社交媒体上高调声援Ripple,对抗监管威胁。面对SEC的指控,他们集体发声,质疑政府选择性执法,声称以太坊当年发行却“逍遥法外”,只有Ripple遭到不公对待coindesk.com。正如《福布斯》的评论所言:没人预料到愤怒的加密散户投资者会掀起法律、政治和社交媒体领域的‘海啸式’反击,痛斥监管机构背弃了保护投资者的承诺crypto-law.us。这种草根抵抗监管的话语体系迅速形成:XRP持有者不但在网上掀起舆论风暴,还采取实际行动向SEC施压。他们发起了请愿,抨击SEC背离保护投资者初衷、诉讼给个人投资者带来巨大伤害,号召停止对Ripple的上诉纠缠——号称这是在捍卫全球加密用户的共同利益bitget.com。一场由民间主导的反监管运动就此拉开帷幕。
Ripple公司则选择背水一战,拒绝和解,在法庭上与SEC针锋相对地鏖战了近三年之久。Ripple坚称XRP并非证券,不应受到SEC管辖,即使面临沉重法律费用和业务压力也不妥协。2023年,这场持久战迎来了标志性转折:美国法庭作出初步裁决,认定XRP在二级市场的流通不构成证券coindesk.com。这一胜利犹如给沉寂已久的XRP注入强心针——消息公布当天XRP价格飙涨近一倍,盘中一度逼近1美元大关coindesk.com。沉重监管阴影下苟延残喘的项目,凭借司法层面的突破瞬间重获生机。这不仅是Ripple的胜利,更被支持者视为整个加密行业对SEC强权的一次胜仗。
XRP的对抗路线与某些“主动合规”的项目形成了鲜明对比。 稳定币USDC的发行方Circle、美国最大合规交易所Coinbase等选择了一条迎合监管的道路:它们高调拥抱现行法规,希望以合作换取生存空间。然而现实却给了它们沉重一击。USDC稳定币在监管风波中一度失去美元锚定,哪怕Circle及时披露储备状况也无法阻止恐慌蔓延,大批用户迅速失去信心,短时间内出现数十亿美元的赎回潮blockworks.co。Coinbase则更为直接:即便它早已注册上市、反复向监管示好,2023年仍被SEC指控为未注册证券交易所reuters.com,卷入漫长诉讼漩涡。可见,在迎合监管的策略下,这些机构非但未能换来监管青睐,反而因官司缠身或用户流失而丧失市场信任。 相比之下,XRP以对抗求生存的路线反而赢得了投资者的眼光:价格的涨跌成为社区投票的方式,抗争的勇气反过来强化了市场对它的信心。
同样引人深思的是另一种迥异的治理路径:技术至上的链上治理。 以MakerDAO为代表的去中心化治理模式曾被寄予厚望——MKR持币者投票决策、算法维持稳定币Dai的价值,被视为“代码即法律”的典范。然而,这套纯技术治理在市场层面却未能形成广泛认同,亦无法激发群体性的情绪动员。复杂晦涩的机制使得普通投资者难以参与其中,MakerDAO的治理讨论更多停留在极客圈子内部,在社会大众的政治对话中几乎听不见它的声音。相比XRP对抗监管所激发的铺天盖地关注,MakerDAO的治理实验显得默默无闻、难以“出圈”。这也说明,如果一种治理实践无法连接更广泛的利益诉求和情感共鸣,它在社会政治层面就难以形成影响力。
XRP之争的政治象征意义由此凸显: 它展示了一条“以市场对抗国家”的斗争路线,即通过代币价格的集体行动来回应监管权力的施压。在这场轰动业界的对决中,价格即是抗议的旗帜,涨跌映射着政治立场。XRP对SEC的胜利被视作加密世界向旧有权力宣告的一次胜利:资本市场的投票器可以撼动监管者的强权。这种“价格即政治”的张力,正是Crypto世界前所未有的社会实验:去中心化社区以市场行为直接对抗国家权力,在无形的价格曲线中凝聚起政治抗争的力量,向世人昭示加密货币不仅有技术和资本属性,更蕴含着不可小觑的社会能量和政治意涵。
不可归零的政治资本
Meme 币的本质并非廉价或易造,而在于其构建了一种“无法归零”的社群生存结构。 对于传统观点而言,多数 meme 币只是短命的投机游戏:价格暴涨暴跌后一地鸡毛,创始人套现跑路,投资者血本无归,然后“大家转去炒下一个”theguardian.com。然而,meme 币社群的独特之处在于——失败并不意味着终结,而更像是运动的逗号而非句号。一次币值崩盘后,持币的草根们往往并未散去;相反,他们汲取教训,准备东山再起。这种近乎“不死鸟”的循环,使得 meme 币运动呈现出一种数字政治循环的特质:价格可以归零,但社群的政治热情和组织势能不归零。正如研究者所指出的,加密领域中的骗局、崩盘等冲击并不会摧毁生态,反而成为让系统更加强韧的“健康应激”,令整个行业在动荡中变得更加反脆弱cointelegraph.com。对应到 meme 币,每一次暴跌和重挫,都是社群自我进化、卷土重来的契机。这个去中心化群体打造出一种自组织的安全垫,失败者得以在瓦砾上重建家园。对于草根社群、少数派乃至体制的“失败者”而言,meme 币提供了一个永不落幕的抗争舞台,一种真正反脆弱的政治性。正因如此,我们看到诸多曾被嘲笑的迷因项目屡败屡战:例如 Dogecoin 自2013年问世后历经八年沉浮,早已超越玩笑属性,成为互联网史上最具韧性的迷因之一frontiersin.org;支撑 Dogecoin 的正是背后强大的迷因文化和社区意志,它如同美国霸权支撑美元一样,为狗狗币提供了“永不中断”的生命力frontiersin.org。
“复活权”的数字政治意涵
这种“失败-重生”的循环结构蕴含着深刻的政治意涵:在传统政治和商业领域,一个政党选举失利或一家公司破产往往意味着清零出局,资源散尽、组织瓦解。然而在 meme 币的世界,社群拥有了一种前所未有的“复活权”。当项目崩盘,社区并不必然随之消亡,而是可以凭借剩余的人心和热情卷土重来——哪怕换一个 token 名称,哪怕重启一条链,运动依然延续。正如 Cheems 项目的核心开发者所言,在几乎无人问津、技术受阻的困境下,大多数人可能早已卷款走人,但 “CHEEMS 社区没有放弃,背景、技术、风投都不重要,重要的是永不言弃的精神”cointelegraph.com。这种精神使得Cheems项目起死回生,社区成员齐声宣告“我们都是 CHEEMS”,共同书写历史cointelegraph.com。与传统依赖风投和公司输血的项目不同,Cheems 完全依靠社区的信念与韧性存续发展,体现了去中心化运动的真谛cointelegraph.com。这意味着政治参与的门槛被大大降低:哪怕没有金主和官方背书,草根也能凭借群体意志赋予某个代币新的生命。对于身处社会边缘的群体来说,meme 币俨然成为自组织的安全垫和重新集结的工具。难怪有学者指出,近期涌入meme币浪潮的主力,正是那些对现实失望但渴望改变命运的年轻人theguardian.com——“迷茫的年轻人,想要一夜暴富”theguardian.com。meme币的炒作表面上看是投机赌博,但背后蕴含的是草根对既有金融秩序的不满与反抗:没有监管和护栏又如何?一次失败算不得什么,社区自有后路和新方案。这种由底层群众不断试错、纠错并重启的过程,本身就是一种数字时代的新型反抗运动和群众动员机制。
举例而言,Terra Luna 的沉浮充分展现了这种“复活机制”的政治力量。作为一度由风投资本热捧的项目,Luna 币在2022年的崩溃本可被视作“归零”的失败典范——稳定币UST瞬间失锚,Luna币价归零,数十亿美元灰飞烟灭。然而“崩盘”并没有画下休止符。Luna的残余社区拒绝承认失败命运,通过链上治理投票毅然启动新链,“复活”了 Luna 代币,再次回到市场交易reuters.com。正如 Terra 官方在崩盘后发布的推文所宣称:“我们力量永在社区,今日的决定正彰显了我们的韧性”reuters.com。事实上,原链更名为 Luna Classic 后,大批所谓“LUNC 军团”的散户依然死守阵地,誓言不离不弃;他们自发烧毁巨量代币以缩减供应、推动技术升级,试图让这个一度归零的项目重新燃起生命之火binance.com。失败者并未散场,而是化作一股草根洪流,奋力托举起项目的残迹。经过迷因化的叙事重塑,这场从废墟中重建价值的壮举,成为加密世界中草根政治的经典一幕。类似的案例不胜枚举:曾经被视为笑话的 DOGE(狗狗币)正因多年社群的凝聚而跻身主流币种,总市值一度高达数百亿美元,充分证明了“民有民享”的迷因货币同样可以笑傲市场frontiersin.org。再看最新的美国政治舞台,连总统特朗普也推出了自己的 meme 币 $TRUMP,号召粉丝拿真金白银来表达支持。该币首日即从7美元暴涨至75美元,两天后虽回落到40美元左右,但几乎同时,第一夫人 Melania 又发布了自己的 $Melania 币,甚至连就职典礼的牧师都跟风发行了纪念币theguardian.com!显然,对于狂热的群众来说,一个币的沉浮并非终点,而更像是运动的换挡——资本市场成为政治参与的新前线,你方唱罢我登场,meme 币的群众动员热度丝毫不减。值得注意的是,2024年出现的 Pump.fun 等平台更是进一步降低了这一循环的技术门槛,任何人都可以一键生成自己的 meme 币theguardian.com。这意味着哪怕某个项目归零,剩余的社区完全可以借助此类工具迅速复制一个新币接力,延续集体行动的火种。可以说,在 meme 币的世界里,草根社群获得了前所未有的再生能力和主动权,这正是一种数字时代的群众政治奇观:失败可以被当作梗来玩,破产能够变成重生的序章。
价格即政治:群众投机的新抗争
meme 币现象的兴盛表明:在加密时代,价格本身已成为一种政治表达。这些看似荒诞的迷因代币,将金融市场变成了群众宣泄情绪和诉求的另一个舞台。有学者将此概括为“将公民参与直接转化为了投机资产”cdn-brighterworld.humanities.mcmaster.ca——也就是说,社会运动的热情被注入币价涨跌,政治支持被铸造成可以交易的代币。meme 币融合了金融、技术与政治,通过病毒般的迷因文化激发公众参与,形成对现实政治的某种映射cdn-brighterworld.humanities.mcmaster.caosl.com。当一群草根投入全部热忱去炒作一枚毫无基本面支撑的币时,这本身就是一种大众政治动员的体现:币价暴涨,意味着一群人以戏谑的方式在向既有权威叫板;币价崩盘,也并不意味着信念的消亡,反而可能孕育下一次更汹涌的造势。正如有分析指出,政治类 meme 币的出现前所未有地将群众文化与政治情绪融入市场行情,价格曲线俨然成为民意和趋势的风向标cdn-brighterworld.humanities.mcmaster.ca。在这种局面下,投机不再仅仅是逐利,还是一种宣示立场、凝聚共识的过程——一次次看似荒唐的炒作背后,是草根对传统体制的不服与嘲讽,是失败者拒绝认输的呐喊。归根结底,meme 币所累积的,正是一种不可被归零的政治资本。价格涨落之间,群众的愤怒、幽默与希望尽显其中;这股力量不因一次挫败而消散,反而在市场的循环中愈发壮大。也正因如此,我们才说“价格即政治”——在迷因币的世界里,价格不只是数字,更是人民政治能量的晴雨表,哪怕归零也终将卷土重来。cdn-brighterworld.humanities.mcmaster.caosl.com
全球新兴现象:伊斯兰金融的入场
当Crypto在西方世界掀起市场治政的狂潮时,另一股独特力量也悄然融入这一场域:伊斯兰金融携其独特的道德秩序,开始在链上寻找存在感。长期以来,伊斯兰金融遵循着一套区别于世俗资本主义的原则:禁止利息(Riba)、反对过度投机(Gharar/Maysir)、强调实际资产支撑和道德投资。当这些原则遇上去中心化的加密技术,会碰撞出怎样的火花?出人意料的是,这两者竟在“以市场行为表达价值”这个层面产生了惊人的共鸣。伊斯兰金融并不拒绝市场机制本身,只是为其附加了道德准则;Crypto则将市场机制推向了政治高位,用价格来表达社群意志。二者看似理念迥异,实则都承认市场行为可以也应当承载社会价值观。这使得越来越多金融与政治分析人士开始关注:当虔诚的宗教伦理遇上狂野的加密市场,会塑造出何种新范式?
事实上,穆斯林世界已经在探索“清真加密”的道路。一些区块链项目致力于确保协议符合伊斯兰教法(Sharia)的要求。例如Haqq区块链发行的伊斯兰币(ISLM),从规则层面内置了宗教慈善义务——每发行新币即自动将10%拨入慈善DAO,用于公益捐赠,以符合天课(Zakat)的教义nasdaq.comnasdaq.com。同时,该链拒绝利息和赌博类应用,2022年还获得了宗教权威的教令(Fatwa)认可其合规性nasdaq.com。再看理念层面,伊斯兰经济学强调货币必须有内在价值、收益应来自真实劳动而非纯利息剥削。这一点与比特币的“工作量证明”精神不谋而合——有人甚至断言法定货币无锚印钞并不清真,而比特币这类需耗费能源生产的资产反而更符合教法初衷cointelegraph.com。由此,越来越多穆斯林投资者开始以道德投资的名义进入Crypto领域,将资金投向符合清真原则的代币和协议。
这种现象带来了微妙的双重合法性:一方面,Crypto世界原本奉行“价格即真理”的世俗逻辑,而伊斯兰金融为其注入了一股道德合法性,使部分加密资产同时获得了宗教与市场的双重背书;另一方面,即便在遵循宗教伦理的项目中,最终决定成败的依然是市场对其价值的认可。道德共识与市场共识在链上交汇,共同塑造出一种混合的新秩序。这一全球新兴现象引发广泛议论:有人将其视为金融民主化的极致表现——不同文化价值都能在市场平台上表达并竞争;也有人警惕这可能掩盖新的风险,因为把宗教情感融入高风险资产,既可能凝聚强大的忠诚度,也可能在泡沫破裂时引发信仰与财富的双重危机。但无论如何,伊斯兰金融的入场使Crypto的政治版图更加丰盈多元。从华尔街交易员到中东教士,不同背景的人们正通过Crypto这个奇特的舞台,对人类价值的表达方式进行前所未有的实验。
升华结语:价格即政治的新直觉
回顾比特币问世以来的这段历程,我们可以清晰地看到一条演进的主线:先有货币革命,后有政治发明。比特币赋予了人类一种真正自主的数字货币,而Crypto在此基础上完成的,则是一项前所未有的政治革新——它让市场价格行为承担起了类似政治选票的功能,开创了一种“价格即政治”的新直觉。在这个直觉下,市场不再只是冷冰冰的交易场所;每一次资本流动、每一轮行情涨落,都被赋予了社会意义和政治涵义。买入即表态,卖出即抗议,流动性的涌入或枯竭胜过千言万语的陈情。Crypto世界中,K线图俨然成为民意曲线,行情图就是政治晴雨表。决策不再由少数权力精英关起门来制定,而是在全球无眠的交易中由无数普通人共同谱写。这样的政治形式也许狂野,也许充满泡沫和噪音,但它不可否认地调动起了广泛的社会参与,让原本疏离政治进程的个体通过持币、交易重新找回了影响力的幻觉或实感。
“价格即政治”并非一句简单的口号,而是Crypto给予世界的全新想象力。它质疑了传统政治的正统性:如果一串代码和一群匿名投资者就能高效决策资源分配,我们为何还需要繁冗的官僚体系?它也拷问着自身的内在隐忧:当财富与权力深度绑定,Crypto政治如何避免堕入金钱统治的老路?或许,正是在这样的矛盾和张力中,人类政治的未来才会不断演化。Crypto所开启的,不仅是技术乌托邦或金融狂欢,更可能是一次对民主形式的深刻拓展和挑战。这里有最狂热的逐利者,也有最理想主义的社群塑梦者;有一夜暴富的神话,也有瞬间破灭的惨痛。而这一切汇聚成的洪流,正冲撞着工业时代以来既定的权力谱系。
当我们再次追问:Crypto究竟是什么? 或许可以这样回答——Crypto是比特币之后,人类完成的一次政治范式的试验性跃迁。在这里,价格行为化身为选票,资本市场演化为广场,代码与共识共同撰写“社会契约”。这是一场仍在进行的文明实验:它可能无声地融入既有秩序,也可能剧烈地重塑未来规则。但无论结局如何,如今我们已经见证:在比特币发明真正的货币之后,Crypto正在发明真正属于21世纪的政治。它以数字时代的语言宣告:在链上,价格即政治,市场即民意,代码即法律。这,或许就是Crypto带给我们的最直观而震撼的本质启示。
参考资料:
-
中本聪. 比特币白皮书: 一种点对点的电子现金系统. (2008)bitcoin.org
-
Arkham Intelligence. Ethereum vs Ethereum Classic: Understanding the Differences. (2023)arkhamintelligence.com
-
Binance Square (@渔神的加密日记). 狗狗币价格为何上涨?背后的原因你知道吗?binance.com
-
Cointelegraph中文. 特朗普的迷因币晚宴预期内容揭秘. (2025)cn.cointelegraph.com
-
慢雾科技 Web3Caff (@Lisa). 风险提醒:从 LIBRA 看“政治化”的加密货币骗局. (2025)web3caff.com
-
Nasdaq (@Anthony Clarke). How Cryptocurrency Aligns with the Principles of Islamic Finance. (2023)nasdaq.comnasdaq.com
-
Cointelegraph Magazine (@Andrew Fenton). DeFi can be halal but not DOGE? Decentralizing Islamic finance. (2023)cointelegraph.com
-
-
 @ eb0157af:77ab6c55
2025-05-24 18:01:14
@ eb0157af:77ab6c55
2025-05-24 18:01:14Vivek Ramaswamy’s company bets on distressed bitcoin claims as its Bitcoin treasury strategy moves forward.
Strive Enterprises, an asset management firm co-founded by Vivek Ramaswamy, is exploring the acquisition of distressed bitcoin claims, with particular interest in around 75,000 BTC tied to the Mt. Gox bankruptcy estate. This move is part of the company’s broader strategy to build a Bitcoin treasury ahead of its planned merger with Asset Entities.
According to a document filed on May 20 with the Securities and Exchange Commission, Strive has partnered with 117 Castell Advisory Group to “identify and evaluate” distressed Bitcoin claims with confirmed legal judgments. Among these are approximately 75,000 BTC connected to Mt. Gox, with an estimated market value of $8 billion at current prices.
Essentially, Strive aims to acquire rights to bitcoins currently tied up in legal disputes, which can be purchased at a discount by those willing to take on the risk and wait for eventual recovery.
In a post on X, Strive’s CFO, Ben Pham, stated:
“Strive intends to use all available mechanisms, including novel financial strategies not used by other Bitcoin treasury companies, to maximize its exposure to the asset.”
The company also plans to buy cash at a discount by merging with publicly traded companies holding more cash than their stock value, using the excess funds to purchase additional Bitcoin.
Mt. Gox, the exchange that collapsed in 2014, is currently in the process of repaying creditors, with a deadline set for October 31, 2025.
In its SEC filing, Strive declared:
“This strategy is intended to allow Strive the opportunity to purchase Bitcoin exposure at a discount to market price, enhancing Bitcoin per share and supporting its goal of outperforming Bitcoin over the long run.”
At the beginning of May, Strive announced its merger plan with Asset Entities, a deal that would create the first publicly listed asset management firm focused on Bitcoin. The resulting company aims to join the growing number of firms adopting a Bitcoin treasury strategy.
The corporate treasury trend
Strive’s initiative to accumulate bitcoin mirrors that of other companies like Strategy and Japan’s Metaplanet. On May 19, Strategy, led by Michael Saylor, announced the purchase of an additional 7,390 BTC for $764.9 million, raising its total holdings to 576,230 BTC. On the same day, Metaplanet revealed it had acquired another 1,004 BTC, increasing its total to 7,800 BTC.
The post Bitcoin in Strive’s sights: 75,000 BTC from Mt. Gox among its targets appeared first on Atlas21.
-
 @ eb0157af:77ab6c55
2025-05-24 18:01:13
@ eb0157af:77ab6c55
2025-05-24 18:01:13According to the ECB Executive Board member, the launch of the digital euro depends on the timing of the EU regulation.
The European Central Bank (ECB) is making progress in preparing for the digital euro. According to Piero Cipollone, ECB Executive Board member and coordinator of the project, the technical phase “is proceeding quickly and on schedule,” but moving to operational implementation still requires political approval of the regulation at the European level.
Speaking at the ‘Voices on the Future’ event organized by Ansa and Asvis, Cipollone outlined a possible timeline:
“If the regulation is approved at the start of 2026 — in the best-case scenario for the European legislative process — we could see the first transactions with the digital euro by mid-2028.”
Cipollone also highlighted Europe’s current dependence on electronic payment systems managed by non-European companies:
“Today in Europe, whenever we don’t use cash, any transaction online or at the supermarket has to go through credit cards, with their fees. The payment system relies on companies that aren’t based in Europe. You can see why it would make sense to have a system fully under our control.”
For the ECB board member, the digital euro would act as a direct alternative to cash in the digital world, working like “a banknote you can spend anywhere in Europe for any purpose.”
The digital euro project is part of the ECB’s broader strategy to strengthen the independence of Europe’s financial system. According to Cipollone and the Central Bank, Europe’s digital currency would be a key step toward greater autonomy in electronic payments, reducing reliance on infrastructure and services outside the European Union.
The post ECB: digital euro by mid-2028, says Cipollone appeared first on Atlas21.
-
 @ eb0157af:77ab6c55
2025-05-24 18:01:12
@ eb0157af:77ab6c55
2025-05-24 18:01:12A new study reveals: 4 out of 5 Americans would like the US to convert some of its gold into Bitcoin.
A recent survey conducted by the Nakamoto Project revealed that a majority of Americans support converting a portion of the United States’ gold reserves into Bitcoin. The survey, carried out online by Qualtrics between February and March 2025, involved 3,345 participants with demographic characteristics representative of US census standards. Most respondents expressed a desire to convert between 1% and 30% of the gold reserves into BTC.
Troy Cross, co-founder of the Nakamoto Project, stated:
“When given a slider and asked to advise the US government on the right proportion of Bitcoin and gold, subjects were very reluctant to put that slider on 0% Bitcoin and 100% gold. Instead, they settled around 10% Bitcoin.”
One significant finding from the research is the correlation between age and openness to Bitcoin: younger respondents showed a greater inclination toward the cryptocurrency compared to older generations.
A potential US strategy
Bo Hines, a White House advisor, is promoting an initiative for the Treasury Department to acquire Bitcoin by selling off a portion of its gold. Under the proposed plan, the government could acquire up to 1 million BTC over the next five years.
To finance these purchases, the government plans to sell Federal Reserve gold certificates. The proposal aligns with Senator Cynthia Lummis’ 2025 Bitcoin Act, which aims to declare Bitcoin a critical national strategic asset.
Currently, the United States holds 8,133 metric tons of gold, valued at over $830 billion, and about 200,000 BTC, valued at $21 billion.
The post The majority in the US wants to convert part of the gold reserves into Bitcoin appeared first on Atlas21.
-
 @ eb0157af:77ab6c55
2025-05-24 18:01:11
@ eb0157af:77ab6c55
2025-05-24 18:01:11The exchange reveals the extent of the breach that occurred last December as federal authorities investigate the recent data leak.
Coinbase has disclosed that the personal data of 69,461 users was compromised during the breach in December 2024, according to documentation filed with the Maine Attorney General’s Office.
The disclosure comes after Coinbase announced last week that a group of hackers had demanded a $20 million ransom, threatening to publish the stolen data on the dark web. The attackers allegedly bribed overseas customer service agents to extract information from the company’s systems.
Coinbase had previously stated that the breach affected less than 1% of its user base, compromising KYC (Know Your Customer) data such as names, addresses, and email addresses. In a filing with the U.S. Securities and Exchange Commission (SEC), the company clarified that passwords, private keys, and user funds were not affected.
Following the reports, the SEC has reportedly opened an official investigation to verify whether Coinbase may have inflated user metrics ahead of its 2021 IPO. Separately, the Department of Justice is investigating the breach at Coinbase’s request, according to CEO Brian Armstrong.
Meanwhile, Coinbase has faced criticism for its delayed response to the data breach. Michael Arrington, founder of TechCrunch, stated that the stolen data could cause irreparable harm. In a post on X, Arrington wrote:
“The human cost, denominated in misery, is much larger than the $400m or so they think it will actually cost the company to reimburse people. The consequences to companies who do not adequately protect their customer information should include, without limitation, prison time for executives.”
Coinbase estimates the incident could cost between $180 million and $400 million in remediation expenses and customer reimbursements.
Arrington also condemned KYC laws as ineffective and dangerous, calling on both regulators and companies to better protect user data:
“Combining these KYC laws with corporate profit maximization and lax laws on penalties for hacks like these means these issues will continue to happen. Both governments and corporations need to step up to stop this. As I said, the cost can only be measured in human suffering.”
The post Coinbase: 69,461 users affected by December 2024 data breach appeared first on Atlas21.
-
 @ eb0157af:77ab6c55
2025-05-24 18:01:10
@ eb0157af:77ab6c55
2025-05-24 18:01:10Bitcoin adoption will come through businesses: neither governments nor banks will lead the revolution.
In recent years, it’s undeniable that Bitcoin has ceased to be just a radical idea born from the minds of cypherpunks. It is now recognized across the board as a global asset, discussed in the upper echelons of finance, accepted even on Wall Street, purchased by banking groups and included as a “strategic reserve” by some nations.
However, the general perception that hovers today regarding Bitcoin’s diffusion is still that of minimal adoption, almost insignificant. Bitcoin exists, certainly, but in fact it is not being used. It is rarely possible to pay in satoshis in commercial establishments. Demand is still extremely low.
Furthermore, the debate on Bitcoin is still practically absent: excluding some local events, some niche media outlets or some timid discussion, today Bitcoin is in fact excluded from general interest. The level of understanding and knowledge of the phenomenon is certainly still very low.
Yet, Bitcoin represents an unprecedented technological improvement, capable of solving many problems inherent in the fiat system in which we live. What could facilitate its diffusion?
Bitcoin becomes familiar when businesses adopt it
When talking about Bitcoin adoption, many look to States. They imagine governments that legislate or accumulate Bitcoin as a “strategic reserve,” or banks perceived as forward-thinking that would lead technological change, opening up to innovation. But the reality is different: bureaucracy, political constraints, and fear of losing control inherently prevent States and central banks from being pioneers.
What really drives Bitcoin adoption are not States, but businesses. It is the forward-looking entrepreneurs, innovative startups and – eventually – even large multinational companies that decide to integrate Bitcoin into their operating systems that drive adoption. Indeed, the business world has always played a key role in the adoption of new technologies. This was the case, for example, with the internet, e-commerce, mobile telephony, and the cloud. It will also be the case with Bitcoin.
Unlike a State, when a company adopts Bitcoin, it does so for concrete reasons: efficiency, savings, protection, access to new markets, independence from traditional banking circuits, or bureaucratic streamlining. It is a rational choice, not an ideological one, dictated by the intent to improve one’s competitiveness against the competition to survive in the market.
What is currently missing to facilitate adoption is, in all likelihood, a significant number of businesses that have decided to integrate Bitcoin into their company systems.
Bitcoin becomes “normal” when it is integrated into the operational flow of businesses. Holding and framing bitcoin on the balance sheet, paying an invoice, paying salaries to employees in satoshis, making value transfers globally thanks to the blockchain, allowing customers to pay via Lightning Network… when all this becomes possible with the same simplicity with which we use the euro or the dollar, Bitcoin stops being alternative and becomes the standard.
Businesses are not just users. They are adoption multipliers. When a company chooses Bitcoin, it is automatically proposing it to customers, employees, suppliers, and institutional stakeholders. Each business adoption equals tens, hundreds, or thousands of new eyes on Bitcoin.
People, after all, trust what they see every day: if your trusted restaurant accepts bitcoin, or if your favorite e-commerce platform uses it to receive international payments, or if your colleague receives it as a salary, then Bitcoin no longer appears to be a mysterious object. It finally begins to be perceived as a real, useful, and functioning tool.
The integration of a technology in companies helps make it understandable, accessible, and legitimate in the eyes of the public. This is how distrust is overcome: by making Bitcoin visible in daily life.
Bitcoin and businesses today
A River Financial report estimates that as of May 2025, only 5% of bitcoin is currently owned by private businesses. A still very small number.

According to research by River, in May 2025 businesses hold just over a million btc (about 5% of available monetary units). More than two-thirds of bitcoin (68.2%) are in the hands of private individuals.
To promote Bitcoin adoption, it is necessary today to support businesses in integrating this standard, leveraging all its enormous opportunities. Among others, this technology allows for fast, economical, and global payments. It eliminates intermediaries, increases transparency and security in value transfers. It removes bureaucratic frictions and allows opening up to a new global market.
Every sector can benefit from Bitcoin: e-commerce, tourism, industry, restaurants, professional services, or any other business. Bitcoin revolutionizes the concept of money, and money is a transversal working tool.
We are still at the beginning, but several signals are encouraging. According to a study by Bitwise and reported by Atlas21, in the first quarter of 2025, a growing number of US companies (+16.11% compared to the previous one) are including Bitcoin in their balance sheets, not just as a financial bet, but as a long-term strategy to protect their assets and access a decentralized monetary system to transfer value worldwide without resorting to financial intermediaries.
Who is driving the change?
Echoing the words of Roy Sheinfeld, CEO of Breez, the true potential of Bitcoin will be unleashed first and foremost from the work of developers, the true architects in designing and refining tools that are increasingly simple and intuitive to use for anyone, regardless of level of expertise. It is the developers – Roy rightly argued – who will enable us to “conquer the world.”
But probably that’s not enough: the next step is to make Bitcoin a globally accepted technological standard, changing its perception towards the general public. And this is where businesses come into play.
Guided by the market, technological innovation, and the desire to meet user demands, entrepreneurs today represent the fulcrum to accelerate the monetary transition from the current fiat system towards the Bitcoin standard. It is entrepreneurs who transform innovations from opportunities for a few to a reality shared by many.
The adoption of Bitcoin will therefore not arise from a sudden event, nor from the exclusive fruit of enthusiasts’ enthusiasm or from arbitrary political choices decreed by States or regulators.
The future of Bitcoin is built in the places where value is created every day: in companies, in their systems, and in their strategic decisions.
“If we conquer developers, we conquer the world. If we conquer businesses, we conquer adoption.”
The post The key to Bitcoin adoption is businesses appeared first on Atlas21.
-
 @ eb0157af:77ab6c55
2025-05-24 18:01:09
@ eb0157af:77ab6c55
2025-05-24 18:01:09Governor Abbott will have to decide whether to sign the bill establishing a bitcoin reserve for the state.
Texas could become the third U.S. state to set up a strategic bitcoin reserve, following the approval of Senate Bill 21 by the state House, with 101 votes in favor and 42 against.
Lee Bratcher, founder and president of the Texas Blockchain Council, expressed confidence that Governor Greg Abbott will sign the legislative measure. In an interview with The Block, Bratcher said:
“I’ve talked to the governor about this personally, and I think he wants to see Texas lead in this way.”
The bill is expected to reach the governor’s desk within a week or two, according to Bratcher’s projections. If signed, Texas would follow in the footsteps of New Hampshire and Arizona in creating a state-held bitcoin reserve.
Despite Texas ranking as the world’s eighth-largest economy — ahead of many nations — the initial approach to the reserve will be cautious. Bratcher estimates the starting investment will be in the “tens of millions of dollars,” an amount he describes as “modest” for an economy the size of Texas. The responsibility for operational decisions would fall to the state comptroller, who acts as an executive accountant in charge of managing and investing public funds.
“My sense is that it will be in the tens of millions of dollars, which, while it sounds significant, is a very modest amount, for a state the size of Texas.” explained the president of the Texas Blockchain Council.
The road to approval
According to Bratcher, the idea of creating a state bitcoin reserve dates back to 2022 and represents the culmination of years of work by the Texas Blockchain Council. The organization has worked closely with lawmakers who shared the vision of seeing the state accumulate the world’s leading cryptocurrency. Additionally, Texas has long been home to numerous bitcoin mining companies.
The post Texas one step away from a bitcoin reserve: only the governor’s signature is missing appeared first on Atlas21.
-
 @ eb0157af:77ab6c55
2025-05-24 18:01:08
@ eb0157af:77ab6c55
2025-05-24 18:01:08Bitcoin surpasses gold in the United States: 50 million holders and a dominant role in the global market.
According to a new report by River, for the first time in history, the number of Americans owning bitcoin has surpassed that of gold holders. The analysis reveals that approximately 50 million U.S. citizens currently own the cryptocurrency, while gold owners number 37 million. In fact, 14.3% of Americans own bitcoin, the highest percentage of holders worldwide.

Source: River
The report highlights that 40% of all Bitcoin-focused companies are based in the United States, consolidating America’s dominant position in the sector. Additionally, 40.5% of Bitcoin holders are men aged 31 to 35, followed by 35.9% of men aged 41 to 45. In contrast, only 13.4% of holders are women.

Source: River
Notably, U.S. companies hold 94.8% of all bitcoins owned by publicly traded companies worldwide. According to the report, recent regulatory changes in the U.S. have made the asset more accessible through financial products such as spot ETFs.
The document also shows that American investors increasingly view the cryptocurrency as protection against fiscal instability and inflation, appreciating its limited supply and decentralized governance model.
For River, Bitcoin offers significant practical advantages over gold in the modern digital era. Its ease of custody, cross-border transfer, and liquidity make the cryptocurrency an attractive option for both individual and institutional investors, the report suggests.
The post USA: 50 million Americans own bitcoin appeared first on Atlas21.
-
 @ 04c915da:3dfbecc9
2025-05-20 15:50:48
@ 04c915da:3dfbecc9
2025-05-20 15:50:48For years American bitcoin miners have argued for more efficient and free energy markets. It benefits everyone if our energy infrastructure is as efficient and robust as possible. Unfortunately, broken incentives have led to increased regulation throughout the sector, incentivizing less efficient energy sources such as solar and wind at the detriment of more efficient alternatives.
The result has been less reliable energy infrastructure for all Americans and increased energy costs across the board. This naturally has a direct impact on bitcoin miners: increased energy costs make them less competitive globally.
Bitcoin mining represents a global energy market that does not require permission to participate. Anyone can plug a mining computer into power and internet to get paid the current dynamic market price for their work in bitcoin. Using cellphone or satellite internet, these mines can be located anywhere in the world, sourcing the cheapest power available.
Absent of regulation, bitcoin mining naturally incentivizes the build out of highly efficient and robust energy infrastructure. Unfortunately that world does not exist and burdensome regulations remain the biggest threat for US based mining businesses. Jurisdictional arbitrage gives miners the option of moving to a friendlier country but that naturally comes with its own costs.
Enter AI. With the rapid development and release of AI tools comes the requirement of running massive datacenters for their models. Major tech companies are scrambling to secure machines, rack space, and cheap energy to run full suites of AI enabled tools and services. The most valuable and powerful tech companies in America have stumbled into an accidental alliance with bitcoin miners: THE NEED FOR CHEAP AND RELIABLE ENERGY.
Our government is corrupt. Money talks. These companies will push for energy freedom and it will greatly benefit us all.
-
 @ 04c915da:3dfbecc9
2025-05-20 15:50:22
@ 04c915da:3dfbecc9
2025-05-20 15:50:22There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ bf47c19e:c3d2573b
2025-05-24 17:11:28
@ bf47c19e:c3d2573b
2025-05-24 17:11:28Originalni tekst na bitcoin-balkan.com.
Pregled sadržaja
- Odakle Potiče Bitcoin?
- Koje Probleme Rešava Bitcoin?
- Kako se Bitcoin razvijao u poslednjoj deceniji?
Bitcoin je peer to peer elektronski keš, novi oblik digitalnog novca koji se može prenositi između ljudi ili računara, bez potrebe za učestvovanjem pouzdanog posrednika (kao što je banka) i čije izdavanje nije pod kontrolom nijedne stranke.
Zamislite papirni dolar ili metalni novčić. Kad taj novac date drugoj osobi, ona ne mora da zna ko ste vi.
On samo treba da veruju da novac koji dobiju od vas nije falsifikat. Obično, proveravanje falsifikata „fizičkog“ novca, ljudi rade koristeći samo oči i prste ili koristeći specijalnu opremu za testiranje ukoliko se radi o značajnijoj sumi novca.
Većina plaćanja u našem digitalnom društvu vrši se putem Interneta korišćenjem neke posredničke usluge: kompanije za izdavanje kreditnih kartica poput Visa, snabdevača digitalnih plaćanja kao što je PayPal ili Apple Pay ili mrežne platforme poput WeChat u Kini.
Kretanje ka digitalnom plaćanju sa sobom donosi oslanjanje na nekog centralnog aktera koji mora odobriti i verifikovati svaku uplatu.
Priroda novca se promenila od fizičkog predmeta koji možete da nosite, prenesete i autentifikujete do digitalnih bitova koje mora da čuva i verifikuje treća strana koja kontroliše njihov prenos.
Odricanjem od gotovine u korist „udobnih“ digitalnih plaćanja, mi takođe stvaramo sistem u kome dajemo ogromna ovlašćenja onima koji bi poželeli da nas tlače.
Platforme za digitalno plaćanje postale su osnova distopijskih autoritarnih metoda kontrole, poput onih koje kineska vlada koristi za nadgledanje disidenata i sprečava građane, čije ponašanje im se ne svidja, da kupuju robu i plaćaju usluge.
Bitcoin nudi alternativu centralno kontrolisanom digitalnom novcu sa sistemom koji nam vraća prirodu korišćenja keša – čovek čoveku, ali u digitalnom obliku.
Bitcoin je digitalno sredstvo koje se izdaje i prenosi preko mreže međusobno povezanih računara, od koji svaki od njih samostalno potvrđuje da svi ostali igraju po pravilima.

Bitcoin Mreža
Odakle Potiče Bitcoin?
Bitcoin je izumela osoba ili grupa poznata pod pseudonimom Satoshi Nakamoto, oko 2008. godine.
Niko ne zna Satoshijev identitet, a koliko znamo, oni su nestali i o njima se godinama ništa nije čulo.
11.februara 2009. godine, Satoshi je pisao o ranoj verziji Bitcoin-a na mrežnom forumu za cypherpunkere, ljude koji rade na tehnologiji kriptografije i koji su zabrinuti za privatnost i slobodu pojedinca.
Iako ovo nije prvo zvanično objavljivanje Bitcoin-a, sadrži dobar rezime Satoshi-jevih motiva.
Razvio sam novi P2P sistem e-keša otvorenog koda pod nazivom Bitcoin. Potpuno je decentralizovan, bez centralnog servera ili pouzdanih stranki, jer se sve zasniva na kripto dokazima umesto na poverenju. […]
Osnovni problem konvencionalne valute je potpuno poverenje koje je potrebno za njeno funkcionisanje. Centralnoj banci se mora verovati da neće devalvirati valutu, ali istorija tradicionalnih valuta je puna primera kršenja tog poverenja. Bankama se mora verovati da drže naš novac i prenose ga elektronskim putem, ali one ga daju u talasima kreditnih balona sa delićem rezerve. Moramo im verovati sa našom privatnošću, verovati im da neće dozvoliti da kradljivci identiteta pokradu naše račune. Njihovi ogromni režijski troškovi onemogućavaju mikro plaćanja.
Generaciju ranije, višekorisnički time-sharing računarski sistemi imali su sličan problem. Pre pojave jake enkripcije, korisnici su morali da imaju pouzdanje u zaštitu lozinkom kako bi zaštitili svoje fajlove […]
Tada je jaka enkripcija postala dostupna širokim masama i više nije bilo potrebno poverenje. Podaci bi se mogli osigurati na način koji je fizički bio nemoguć za pristup drugima, bez obzira iz kog razloga, bez obzira koliko je dobar izgovor, bez obzira na sve.
Vreme je da imamo istu stvar za novac. Uz e-valutu zasnovanu na kriptografskom dokazu, bez potrebe da verujete posredniku treće strane, novac može biti siguran i transakcije mogu biti izvršene bez napora. […]
Rešenje Bitcoin-a je korišćenje peer-to-peer mreže za proveru dvostruke potrošnje. Ukratko, mreža radi poput distribuiranog servera vremenskih žigova, obeležavajući prvu transakciju koja je potrošila novčić. Potrebna je prednost prirode informacije koju je lako širiti, ali je teško ugušiti. Za detalje o tome kako to funkcioniše, pogledajte članak o dizajnu na bitcoin.org
Satoshi Nakamoto
Koje Probleme Rešava Bitcoin?
Razdvojimo neke od Satoshi-jevih postova kako bismo uvideli razloge njegove motivacije.
„Razvio sam novi P2P sistem e-keša otvorenog koda.“
P2P je skraćenica za peer to peer i ukazuje na sistem u kojem jedna osoba može da komunicira sa drugom bez ikoga u sredini, kao medjusobno jednaki.
Možete se setiti P2P tehnologija za razmenu datoteka poput Napster-a, Kazaa-e i BitTorrrent-a, koje su prve omogućile ljudima da dele muziku i filmove bez posrednika.
Satoshi je dizajnirao Bitcoin kako bi omogućio ljudima da razmenjuju e-keš, elektronski keš, bez prolaska preko posrednika na približno isti način.
Softver je otvorenog koda, što znači da svako može videti kako funkcioniše i doprineti tome.
Ne treba da verujemo ni u šta što je Satoshi napisao u svom postu o tome kako softver radi.
Možemo pogledati kod i sami proveriti kako to funkcioniše. Štaviše, možemo promeniti funkcionalnost sistema promenom koda.
„Potpuno je decentralizovan, bez centralnog servera ili pouzdanih stranki …“
Satoshi napominje da je sistem decentralizovan kako bi se razlikovao od sistema koji imaju centralnu kontrolu.
Prethodne pokušaje stvaranja digitalne gotovine poput DigiCash-a od strane Davida Chaum-a podržavao je centralni server, računar ili skup računara koji je bio odgovoran za izdavanje i verifikaciju plaćanja pod kontrolom jedne korporacije.
Takve, centralno kontrolisane privatne šeme novca, bile su osuđene na propast; ljudi se ne mogu osloniti na novac koji može nestati kada kompanija prestane sa poslovanjem, bude hakovana, pretrpi pad servera ili je zatvori vlada.
Bitcoin održava mreža pojedinaca i kompanija širom sveta.
Da bi se Bitcoin isključio, bilo bi potrebno isključiti desetine do stotine hiljada računara širom sveta u isto vreme, zauvek, od kojih su mnogi na nepoznatim lokacijama.
Bila bi to beznadežna igra, jer bi svaki napad ove prirode jednostavno podstakao stvaranje novih Bitcoin čvorova ili računara na mreži.
„… sve se zasniva na kripto dokazima umesto na poverenju“
Internet, a u stvari i većina savremenih računarskih sistema, izgrađeni su na kriptografiji, metodi prikrivanja informacija, tako da je može dekodirati samo primalac informacije.
Kako se Bitcoin oslobađa potrebe za poverenjem? Umesto da verujemo nekome ko kaže „Ja sam Alisa“ ili „Imam 10 $ na računu“, možemo koristiti kriptografsku matematiku da bismo izneli iste činjenice na način koji je vrlo lako verifikovati od strane primaoca dokaza ali ga je nemoguće falsifikovati.
Bitcoin u svom dizajnu koristi kriptografsku matematiku kako bi učesnicima omogućio da provere ponašanje svih ostalih učesnika, bez poverenja u bilo koju centralnu stranku.
„Moramo im verovati [bankama] sa našom privatnošću, verovati im da neće dozvoliti da kradljivci identiteta pokradu naše račune“
Za razliku od korišćenja vašeg bankovnog računa, sistema digitalnog plaćanja ili kreditne kartice, Bitcoin omogućava dvema stranama da obavljaju transakcije bez davanje bilo kakvih ličnih podataka.
Centralizovana skladišta potrošačkih podataka koji se čuvaju u bankama, kompanijama sa kreditnim karticama, procesorima plaćanja i vladama, predstavljaju pravu poslasticu za hakere.
Kao dokaz Satoshi-jeve poente služi primer iz 2017. godine kada je Equifax masovono kompromitovan, kada su hakeri ukrali identifikacione i finansijske podatke za više od 140 miliona ljudi.
Bitcoin odvaja finansijske transakcije od stvarnih identiteta.
Na kraju krajeva, kada nekome damo fizički novac, on nema potrebu da zna ko smo, niti treba da brinemo da će nakon naše razmene moći da iskoristi neke informacije koje smo mu dali da ukrade još našeg novca.
Zašto ne bismo očekivali isto, ili čak i bolje, od digitalnog novca?
„Centralnoj banci se mora verovati da neće devalvirati valutu, ali istorija tradicionalnih valuta je puna primera kršenja tog poverenja.“
Pojam tradicionalna valuta, odnosi se na valutu izdatu od strane vlade i centralne banke, koju vlada proglašava zakonskim sredstvom plaćanja.
Istorijski, novac je nastao od stvari koje je bilo teško proizvesti, koje su bile lake za proveravanje i transport, poput školjki, staklenih perli, srebra i zlata.
Kad god bi se nešto koristilo kao novac, postojalo je iskušenje da se stvori više toga.
Ako bi neko pronašao vrhunsku tehnologiju za brzo stvaranje velike količine nečega, ta stvar bi izgubila vrednost.
Evropski naseljenici uspeli su da liše afrički kontinent bogatstva trgujući staklenim perlicama koje su se lako proizvodile za ljudske robove.
Isto se dogodilo sa američkim indijancima, kada su kolonisti otkrili način brze proizvodnje vampum školjki, koje su starosedeoci smatrali retkim.
Vremenom, širom sveta ljudi su shvatili da je samo zlato dovoljno retko da deluje kao novac, bez straha da bi neko drugi mogao da ga stvori u velikim količinama.
Polako smo prešli sa svetske ekonomije koja je koristila zlato kao novac na onu gde su banke izdavale papirne sertifikate kao dokaz posedovanja tog zlata.
Nixon je okončao međunarodnu konvertibilnost američkog dolara u zlato 1971. godine, privremenim rešenjem, koje je ubrzo postalo trajno.
Kraj zlatnog standarda omogućio je vladama i centralnim bankama da imaju punu dozvolu da povećavaju novčanu masu po svojoj volji, razredjujući vrednost svake novčanice u opticaju, poznatije kao umanjenje vrednosti.
Iako je izdata od strane vlade, suštinska tradicionalna valuta je novac koji svi znamo i svakodnevno koristimo, ipak je relativno novo iskustvo u opsegu svetske istorije.
Moramo verovati našim vladama da ne zloupotrebljavaju njegovo štamparije, i ne treba nam puno muke da nadjemo primere kršenja tog poverenja.
U autokratskim i centralno planiranim režimima gde vlada ima prst direktno na mašini za novac, kao što je Venecuela, valuta je postala gotovo bezvredna.
Venecuelanski Bolivar prešao je sa 2 bolivara za 1 američki dolar, koliko je vredeo 2009. godine, na 250.000 bolivara za 1 američki dolar 2019. godine.

Pogledajte koliko novčanica je bilo potrebno za kupovinu piletine u Venecueli posle hiperinflacije.

Satoshi je želeo da ponudi alternativu tradicionalnoj valuti čija se ponuda uvek nepredvidivo širi.
Da bi sprečilo umanjenje vrednosti, Satoshi je dizajnirao novčani sistem gde je zaliha bila fiksna i izdavana po predvidljivoj i nepromenjivoj stopi.
Postojaće samo 21 milion Bitcoin-a.
Međutim, svaki Bitcoin se može podeliti na 100 miliona jedinica koje se sada nazivaju satoshis (sats-ovi), što će činiti ukupno 2,1 kvadriliona satoshi-a u opticaju oko 2140. godine.

Pre Bitcoin-a nije bilo moguće sprečiti beskrajnu reprodukciju digitalnih sredstava.
Kopirati digitalnu knjigu, audio datoteku ili video zapis i poslati ga prijatelju, je jeftino i lako.
Jedini izuzeci od toga su digitalna sredstva koja kontrolišu posrednici.
Na primer, kada iznajmite film sa iTunes-a, možete ga gledati na vašem uređaju samo zato što iTunes kontroliše distribuciju tog filma i može ga zaustaviti nakon perioda njegovog iznajmljivanja.
Slično tome, vaša banka kontroliše vaš digitalni novac. Zadatak banke je da vodi evidenciju koliko novca imate.
Ako ga prenesete nekom drugom, oni će odobriti ili odbiti takav prenos.
Bitcoin je prvi digitalni sistem koji sprovodi oskudicu bez posrednika i prvo je sredstvo poznato čovečanstvu čija je nepromenljiva ponuda i raspored izdavanja poznat unapred.
Ni plemeniti metali poput zlata nemaju ovo svojstvo, jer uvek možemo iskopati sve više i više zlata ukoliko je to isplativo.
Zamislite da otkrijemo asteroid koji sadrži deset puta više zlata nego što ga imamo na zemlji.
Šta bi se dogodilo sa cenom zlata uzimajući u obzir tako obilnu ponudu? Bitcoin je imun na takva otkrića i manipulisanje nabavkom.
Jednostavno je nemoguće proizvesti više od toga (21 miliona).
„Podaci bi se mogli osigurati na način koji je fizički bio nemoguć za pristup drugima, bez obzira iz kog razloga, bez obzira koliko je dobar izgovor, bez obzira na sve. […] Vreme je da imamo istu stvar za novac “
Naše trenutne metode obezbeđivanja novca, poput stavljanja u banku, oslanjaju se na poverenje nekome drugom da će obaviti taj posao.
Poverenje u takvog posrednika ne zahteva samo sigurnost da on neće učiniti nešto zlonamerno ili glupo, već i da vlada neće zapleniti ili zamrznuti vaša sredstva vršeći pritisak na ovog posrednika.
Međutim, videli smo bezbroj puta da vlade mogu, i zaista uskraćuju pristup novcu kada se osećaju ugroženo.
Nekom ko živi u Sjedinjenim Državama ili nekoj drugoj visoko regulisanoj ekonomiji možda zvuči glupo da razmišlja da se probudi sa oduzetim novcem, ali to se događa stalno.
PayPal mi je zamrzao sredstva jednostavno zato par meseci nisam koristio svoj račun.
Trebalo mi je više od nedelju dana da vratim pristup „svom“ novcu.
Srećan sam što živim u Europi, gde bih se bar mogao nadati da ću potražiti neko pravno rešenje ako mi PayPal zamrzne sredstva i gde imam osnovno poverenje da moja vlada i banka neće ukrasti moj novac.
Mnogo gore stvari su se dogodile, i trenutno se dešavaju, u zemljama sa manje slobode.
Banke su se zatvorile tokom kolapsa valuta u Grčkoj.
Banke na Kipru su koristile kaucije da konfiskuju sredstva od svojih klijenata.
Indijska vlada je proglasila određene novčanice bezvrednim.
Bivši SSSR, u kojem sam odrastao, imao je ekonomiju pod kontrolom vlade što je dovelo do ogromnih nestašica robe.
Bilo je nezakonito posedovati strane valute kao što je američki dolar.
Kada smo poželeli da odemo, mojoj porodici je bilo dozvoljeno da zameni samo ograničenu količinu novca po osobi za američke dolare po zvaničnom kursu koji je bio u velikoj meri različit od pravog kursa slobodnog tržišta.
U stvari, vlada nam je oduzela ono malo bogatstva koje smo imali koristeći gvozdeni stisak na ekonomiji i kretanju kapitala.
Autokratske zemlje imaju tendenciju da sprovode strogu ekonomsku kontrolu, sprečavajući ljude da na slobodnom tržištu povuku svoj novac iz banaka, iznesu ga iz zemlje ili da ga razmene u ne još uvek bezvredne valute poput američkog dolara.
To omogućava vladinoj slobodnoj vladavini da primeni sulude ekonomske eksperimente poput socijalističkog sistema SSSR-a.
Bitcoin se ne oslanja na poverenje u treću stranu da bi osigurao vaš novac.
Umesto toga, Bitcoin onemogućava drugima pristup vašim novčićima bez jedinstvenog ključa koji imate samo vi, bez obzira iz kog razloga, bez obzira koliko je dobar izgovor, bez obzira na sve.
Držeći Bitcoin, držite ključeve sopstvene finansijske slobode. Bitcoin razdvaja novac i državu
„Rešenje Bitcoin-a je korišćenje peer-to-peer mreže za proveru dvostruke potrošnje […] poput distribuiranog servera vremenskih žigova, obeležavajući prvu transakciju koja je potrošila novčić“
Mreža se odnosi na ideju da je gomila računara povezana i da mogu međusobno slati poruke.
Reč distribuirano znači da ne postoji centralna stranka koja kontroliše, već da svi učesnici koordiniraju medjusobno kako bi mreža bila uspešna.
U sistemu bez centralne kontrole, bitno je znati da niko ne vara. Ideja dvostruke potrošnje odnosi se na mogućnost trošenja istog novca dva puta.
Fizički novac odlazi iz vaše ruke kad ga potrošite. Međutim, digitalne transakcije se mogu kopirati baš kao muzika ili filmovi.
Kada novac šaljete preko banke, oni se pobrinu da isti novac ne možete da prebacujete dva puta.
U sistemu bez centralne kontrole potreban nam je način da sprečimo ovu vrstu dvostruke potrošnje, koja je u suštini ista kao i falsifikovanje novca.
Satoshi opisuje da učesnici u Bitcoin mreži rade zajedno kako bi vremenski označili (doveli u red) transakcije kako bismo znali šta je bilo prvo.
Zbog toga možemo odbiti sve buduće pokušaje trošenja istog novca.
Satoshi se uhvatio u koštac sa nekoliko zanimljivih tehničkih problema kako bi rešio probleme privatnosti, uništavanja vrednosti i centralne kontrole u trenutnim monetarnim sistemima.
Na kraju je stvorio peer to peer mrežu kojoj se svako mogao pridružiti bez otkrivanja svog identiteta ili potrebe da veruje bilo kom drugom učesniku.
Kako se Bitcoin razvijao u poslednjoj deceniji?
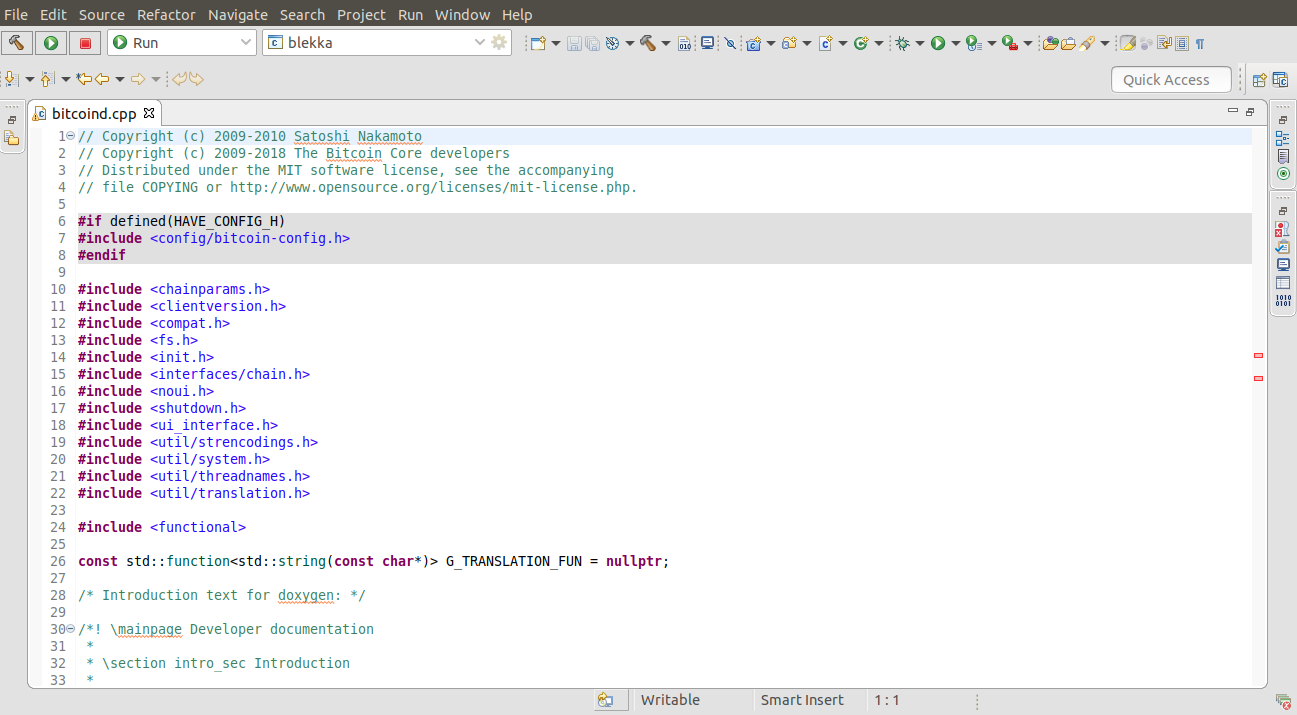
Doprinosi izvornom kodu Bitcoina
Kada je Bitcoin pokrenut, samo nekolicina ljudi ga je koristila i pokrenula Bitcoin softver na svojim računarima za napajanje Bitcoin mreže.
Većina ljudi u to vreme mislila je da je to šala ili da će se otkriti ozbiljni nedostaci u dizajnu sistema koji će ga učiniti neizvodljivim.
Vremenom se mreži pridružilo sve više ljudi koji su pomoću svojih računara dodali sigurnost mreži.
Ljudi su počeli da menjaju Bitcoin-e za robu i usluge, dajući mu stvarnu vrednost. Pojavile su se menjačnice valuta koje su menjale Bitcoin-e za gotovo sve tradicionalne valute na svetu.
Deset godina nakon izuma, Bitcoin koriste milioni ljudi sa desetinama do stotinama hiljada čvorova koji pokreću besplatni Bitcoin softver, koji se razvija od strane stotina dobrovoljaca i kompanija širom sveta.
Bitcoin mreža je porasla kako bi obezbedila vrednost veću od stotine biliona dolara.
Računari koji učestvuju u zaštiti Bitcoin mreže poznati su kao rudari/majneri.
Oni rade u industrijskim operacijama širom sveta, ulažući milione dolara u specijalni rudarski hardver koji radi samo jedno: pobrinuti se da je Bitcoin najsigurnija mreža na planeti.
Rudari troše električnu energiju kako bi transakcije Bitcoin-a učinile sigurnim od modifikacija. Budući da se rudari međusobno takmiče za oskudan broj Bitcoin-a proizvedenih dnevno, oni uvek moraju da pronalaze najjeftinije izvore energije na planeti da bi ostali profitabilni.
Rudari rade na različitim mestima, od hidroelektrana u dalekim krajevima Kine do vetroparkova u Teksasu, do kanadskih naftnih polja koja proizvode gas koji bi u suprotnom bio odzračen ili spaljen u atmosferi.
Iako je Bitcoin popularna tema i o njemu se često raspravlja u medijima, procenjujemo da je samo nekoliko miliona ljudi na svetu počelo da redovno štedi Bitcoin.
Za mnoge ljude, posebno za one koji nikada nisu živeli pod represivnim režimima, ovaj izum novog oblika digitalnog novca izvan kontrole vlade može biti veoma izazovan za razumevanje i prihvatanje.
Zato sam ja ovde. Želim da vam pomognem da razumete Bitcoin i budete gospodar svoje budućnosti!
-
 @ ecda4328:1278f072
2025-05-19 14:41:48
@ ecda4328:1278f072
2025-05-19 14:41:48An honest response to objections — and an answer to the most important question: why does any of this matter?
\ Statement: Deflation is not the enemy, but a natural state in an age of technological progress.\ Criticism: in real macroeconomics, long-term deflation is linked to depressions.\ Deflation discourages borrowers and investors, and makes debt heavier.\ Natural ≠ Safe.
1. “Deflation → Depression, Debt → Heavier”
This is true in a debt-based system. Yes, in a fiat economy, debt balloons to the sky, and without inflation it collapses.
But Bitcoin offers not “deflation for its own sake,” but an environment where you don’t need to be in debt to survive. Where savings don’t melt away.\ Jeff Booth said it clearly:
“Technology is inherently deflationary. Fighting deflation with the printing press is fighting progress.”
You don’t have to take on credit to live in this system. Which means — deflation is not an enemy, but an ally.
💡 People often confuse two concepts:
-
That deflation doesn’t work in an economy built on credit and leverage — that’s true.
-
That deflation itself is bad — that’s a myth.
📉 In reality, deflation is the natural state of a free market when technology makes everything cheaper.
Historical example:\ In the U.S., from the Civil War to the early 1900s, the economy experienced gentle deflation — alongside economic growth, employment expansion, and industrial boom.\ Prices fell: for example, a sack of flour cost \~$1.00 in 1865 and \~$0.50 in 1895 — and there was no crisis, because wages held and productivity increased.
Modern example:\ Consumer electronics over the past 20–30 years are a vivid example of technological deflation:\ – What cost $5,000 in 2000 (e.g., a 720p plasma TV) now costs $300 and delivers 10× better quality.\ – Phones, computers, cameras — all became far more powerful and cheaper at the same time.\ That’s how tech-driven deflation works: you get more for less.
📌 Bitcoin doesn’t make the world deflationary. It just doesn’t fight against deflation, unlike the fiat model that fights to preserve its debt pyramid.\ It stops punishing savers and rewards long-term thinkers.
Even economists often confuse organic tech deflation with crisis-driven (debt) deflation.
\ \ Statement: We’ve never lived in a truly free market — central banks and issuance always existed.\ Criticism: ideological statement.\ A truly “free” market is utopian.\ Banks and monetary issuance emerged in response to crises.\ A market without arbiters is not always fair, especially under imperfect competition.
2. “The Free Market Is a Utopia”
Yes, “pure markets” are rare. But what we have today isn’t regulation — it’s centralized power in the hands of central banks and cartels.
Bitcoin offers rules without rulers. 21 million. No one can change the issuance. It’s not ideology — it’s code instead of trust. And it has worked for 15 years.
\ \ Statement: Inflation is an invisible tax, especially on the poor and working class.\ Criticism: partly true: inflation can reduce debt burden, boost employment.\ The state indexes social benefits. Under stable inflation, compensators can work. Under deflation, things might be worse (mass layoffs, defaults).
3. “Inflation Can Help”
Theoretically — yes. Textbooks say moderate inflation can reduce debt burdens and stimulate consumption and jobs.\ But in practice — it works as a stealth tax, especially on those without assets. The wealthy escape — into real estate, stocks, funds.\ But the poor and working class lose purchasing power because their money is held in cash — and cash devalues.
💬 As Lyn Alden says:
“When your money can’t hold value, you’re forced to become an investor — even if you just want to save and live.”
The state may index pensions or benefits — but always with a lag, and always less than actual price increases.\ If bread rises 15% and your payment increase is 5%, you got poorer, even if the number on paper went up.
💥 We live in an inflationary system of everything:\ – Inflationary money\ – Inflationary products\ – Inflationary content\ – And now even inflationary minds
🧠 This is more than just rising prices — it’s a degradation of reality perception. You’re always rushing, everything loses meaning.\ But when did the system start working against you?
📉 What went wrong after 1971?
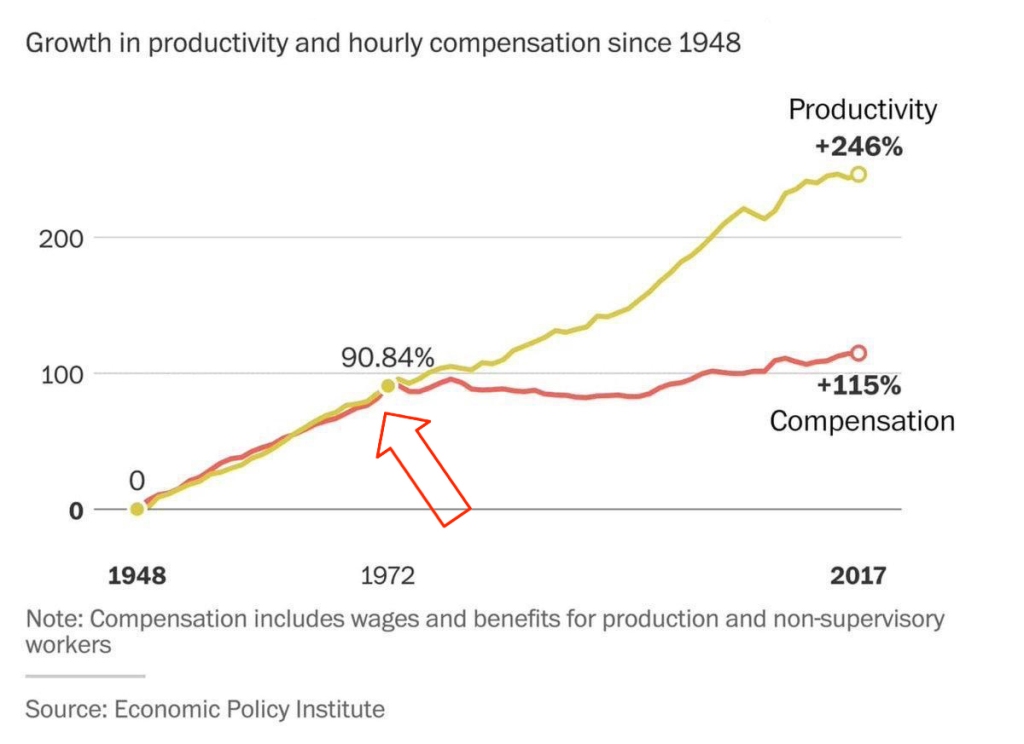 This chart shows that from 1948 to the early 1970s, productivity and wages grew together.\
But after the end of the gold standard in 1971 — the connection broke. Productivity kept rising, but real wages stalled.
This chart shows that from 1948 to the early 1970s, productivity and wages grew together.\
But after the end of the gold standard in 1971 — the connection broke. Productivity kept rising, but real wages stalled.👉 This means: you work more, better, faster — but buy less.
🔗 Source: wtfhappenedin1971.com
When you must spend today because tomorrow it’ll be worth less — that’s rewarding impulse and punishing long-term thinking.
Bitcoin offers a different environment:\ – Savings work\ – Long-term thinking is rewarded\ – The price of the future is calculated, not forced by a printing press
📌 Inflation can be a tool. But in government hands, it became a weapon — a slow, inevitable upward redistribution of wealth.
Indexing is weak compensation if bread is up 15% and your “increase” is only 5%.
\ \ Statement: War is not growth, but a reallocation of resources into destruction.
Criticism: war can spur technological leaps (Internet, GPS, nuclear energy — all from military programs). "Military Keynesianism" was a real model.
4. “War Drives R&D”
Yes, wars sometimes give rise to tech spin-offs: Internet, GPS, nuclear power — all originated from military programs.
But that doesn’t make war a source of progress — it makes tech a byproduct of catastrophe.
“War reallocates resources toward destruction — not growth.”
Progress doesn’t happen because of war — it happens despite it.
If scientific breakthroughs require a million dead and burnt cities — maybe you’ve built your economy wrong.
💬 Even Michael Saylor said:
“If you need war to develop technology — you’ve built civilization wrong.”
No innovation justifies diverting human labor, minds, and resources toward destruction.\ War is always the opposite of efficiency — more is wasted than created.
🧠 Bitcoin, on the other hand, is an example of how real R&D happens without violence.\ No taxes. No army. Just math, voluntary participation, and open-source code.
📌 Military Keynesianism is not a model of progress — it’s a symptom of a sick monetary system that needs destruction to reboot.
Bitcoin shows that coordination without violence is possible.\ This is R&D of a new kind: based not on destruction, but digital creation.
Statement: Bitcoin isn’t “Gold 1.0,” but an improved version: divisible, verifiable, unseizable.
Criticism: Bitcoin has no physical value; "unseizability" is a theory;\ Gold is material and autonomous.
5. “Bitcoin Has No Physical Value”
And gold does? Just because it shines?
Physical form is no guarantee of value.\ Real value lies in: scarcity, reliable transfer, verifiability, and non-confiscatability.
Gold is:\ – Hard to divide\ – Hard to verify\ – Expensive to store\ – Easy to seize
💡 Bitcoin is the first store of value in history that is fully free from physical limitations, and yet:\ – Absolutely scarce (21M, forever)\ – Instantly transferable over the Internet\ – Cryptographically verifiable\ – Controlled by no government
🔑 Bitcoin’s value lies in its liberation from the physical.\ It doesn’t need to be “backed” by gold or oil. It’s backed by energy, mathematics, and ongoing verification.
“Price is what you pay, value is what you get.” — Warren Buffett
When you buy bitcoin, you’re not paying for a “token” — you’re gaining access to a network of distributed financial energy.
⚡️ What are you really getting when you own bitcoin?\ – A key to a digital asset that can’t be faked\ – The ability to send “crystallized energy” anywhere on Earth\ – A role in a new accounting system that runs 24/7/365\ – Freedom: from banks, borders, inflation, and force
📉 Bitcoin doesn’t require physical value — because it creates value:\ Through trust, scarcity, and energy invested in mining.\ And unlike gold, it was never associated with slavery.
Statement: There’s no “income without risk” in Bitcoin: just hold — you preserve; want more — invest, risk, build.
Criticism: contradicts HODL logic; speculation remains dominant behavior.
6. “Speculation Dominates”
For now — yes. That’s normal for the early phase of a new technology. Awareness doesn’t come instantly.
What matters is not the motive of today’s buyer — but what they’re buying.
📉 A speculator may come and go — but the asset remains.\ And this asset is the only one in history that will never exist again. 21 million. Forever.
📌 Look deeper. Bitcoin has:\ – No CEO\ – No central issuer\ – No inflation\ – No “off switch”
💡 It’s not a stock. Not a startup. Not someone’s project.\ It’s a new foundation for trust.\ It’s opting out of a system where freedom is a privilege you’re granted under conditions.
🧠 People say: “Bitcoin can be copied.”\ Theoretically — yes.\ Practically — never.
Here’s what you’d need to recreate Bitcoin:\ – No pre-mine\ – A founder who disappears and never sells\ – No foundation or corporation\ – Tens of thousands of nodes worldwide\ – 701 million terahashes of hash power\ – Thousands of devs writing open protocols\ – Hundreds of global conferences\ – Millions of people defending digital sovereignty\ – All that without a single marketing budget
That’s all.
🔁 Everything else is an imitation, not a creation.\ Just like you can’t “reinvent fire” — Bitcoin can only exist once.
Statements:\ The Russia's '90s weren’t a free market — just anarchic chaos without rights protection.*\ Unlike fiat or even dollars, Bitcoin is the first asset with real defense — from governments, inflation, even thugs.\ And yes, even if your barber asks about Bitcoin — maybe it's not a bubble, but a sign that inflation has already hit everyone.
Criticism: Bitcoin’s protection isn’t universal — it works only with proper handling and isn’t available to all.\ Some just want to “get rich.”\ None of this matters because:
-
Bitcoin’s volatility (-30% in a week, +50% in a month) makes it unusable for price planning or contracts.
-
It can’t handle mass-scale usage.
-
To become currency, geopolitical will is needed — and without the first two, don’t even talk about the third.\ Also: “Bitcoin is too complicated for the average person.”
7. “It’s Too Complex for the Masses”
It’s complex — if you’re using L1 (Layer 1). But even grandmas use Telegram. In El Salvador, schoolkids buy lunch with Lightning. My barber installed Wallet of Satoshi in minutes right in front of me — and I now pay for my haircut via Lightning.
UX is just a matter of time. And it’s improving. Emerging tools:\ Cashu, Fedimint, Fedi, Wallet of Satoshi, Phoenix, Proton Wallet, Swiss Bitcoin Pay, Bolt Card / CoinCorner (NFC cards for Lightning payments).
This is like the internet in 1995:\ It started with modems — now it’s 4K streaming.
8. “Can’t Handle the Load”
A common myth.\ Yes, Bitcoin L1 processes about 7 transactions per second — intentionally. It’s not built to be Visa. It’s a financial protocol, just like TCP/IP is a network protocol. TCP/IP isn’t “fast” or “slow” — the experience depends on the infrastructure built on top: servers, routers, hardware. In the ’90s, it delivered text. Today, it streams Netflix. The protocol didn’t change — the stack did.
Same with Bitcoin: L1 defines rules, security, finality.\ Scaling and speed? That’s the second layer’s job.
To understand scale:
| Network | TPS (Transactions/sec) | | --- | --- | | Visa | up to 24,000 | | Mastercard | \~5,000 | | PayPal | \~193 | | Litecoin | \~56 | | Ethereum | \~20 | | Bitcoin | \~7 |
\ ⚡️ Enter Lightning Network — Bitcoin’s “fast lane.”\ It allows millions of transactions per second, instantly and nearly free.
And it’s not a sidechain.
❗️ Lightning is not a separate network.\ It uses real Bitcoin transactions (2-of-2 multisig). You can close the channel to L1 at any time. It’s not an alternative — it’s a native extension built into Bitcoin.\ Also evolving: Ark, Fedimint, eCash — new ways to scale and add privacy.
📉 So criticizing Bitcoin for “slowness” is like blaming TCP/IP because your old modem won’t stream YouTube.\ The protocol isn’t the problem — it’s the infrastructure.
🛡️ And by the way: Visa crashes more often than Bitcoin.
9. “We Need Geopolitical Will”
Not necessarily. All it takes is the will of the people — and leaders willing to act. El Salvador didn’t wait for G20 approval or IMF blessings. Since 2001, the country had used the US dollar as its official currency, abandoning its own colón. But that didn’t save it from inflation or dependency on foreign monetary policy. In 2021, El Salvador became the first country to recognize Bitcoin as legal tender. Since March 13, 2024, they’ve been purchasing 1 BTC daily, tracked through their public address:
🔗 Address\ 📅 First transaction
This policy became the foundation of their Strategic Bitcoin Reserve (SBR) — a state-led effort to accumulate Bitcoin as a national reserve asset for long-term stability and sovereignty.
Their example inspired others.
In March 2025, U.S. President Donald Trump signed an executive order creating the Strategic Bitcoin Reserve of the USA, to be funded through confiscated Bitcoin and digital assets.\ The idea: accumulate, don’t sell, and strategically expand the reserve — without extra burden on taxpayers.
Additionally, Senator Cynthia Lummis (Wyoming) proposed the BITCOIN Act, targeting the purchase of 1 million BTC over five years (\~5% of the total supply).\ The plan: fund it via revaluation of gold certificates and other budget-neutral strategies.
📚 More: Strategic Bitcoin Reserve — Wikipedia
👉 So no global consensus is required. No IMF greenlight.\ All it takes is conviction — and an understanding that the future of finance lies in decentralized, scarce assets like Bitcoin.
10. “-30% in a week, +50% in a month = not money”
True — Bitcoin is volatile. But that’s normal for new technologies and emerging money. It’s not a bug — it’s a price discovery phase. The world is still learning what this asset is.
📉 Volatility is the price of entry.\ 📈 But the reward is buying the future at a discount.
As Michael Saylor put it:
“A tourist sees Niagara Falls as chaos — roaring, foaming, spraying water.\ An engineer sees immense energy.\ It all depends on your mental model.”
Same with Bitcoin. Speculators see chaos. Investors see structural scarcity. Builders see a new financial foundation.
💡 Now consider gold:
👉 After the U.S. abandoned the gold standard in 1971, gold surged from \~$35 to over $800 in a decade — while suffering wild -40% to -60% crashes along the way.\ \ 📈 Gold Price Chart — Macrotrends\ \ Nobody said, “This can’t be money.” \ Because money is defined not by volatility, but by scarcity, adoption, and trust — which build over time.
📊 The more people save in Bitcoin, the more its volatility fades.
This is a journey — not a fixed state.
We don’t judge the internet by how it worked in 1994.\ So why expect Bitcoin to be the “perfect currency” in 2025?
It grows bottom-up — without regulators’ permission.\ And the longer it survives, the stronger it becomes.
Remember how many times it’s been declared dead.\ And how many times it came back — stronger.
📊 Gold vs. Bitcoin: Supply Comparison
This chart shows the key difference between the two hard assets:
🔹 Gold — supply keeps growing.\ Mining may be limited, but it’s still inflationary.\ Each year, there’s more — with no known cap: new mines, asteroid mining, recycling.
🔸 Bitcoin — capped at 21 million.\ The emission schedule is public, mathematically predictable, and ends completely around 2140.
🧠 Bottom line:\ Gold is good.\ Bitcoin is better — for predictability and scarcity.
💡 As Saifedean Ammous said:
“Gold was the best monetary good… until Bitcoin.”
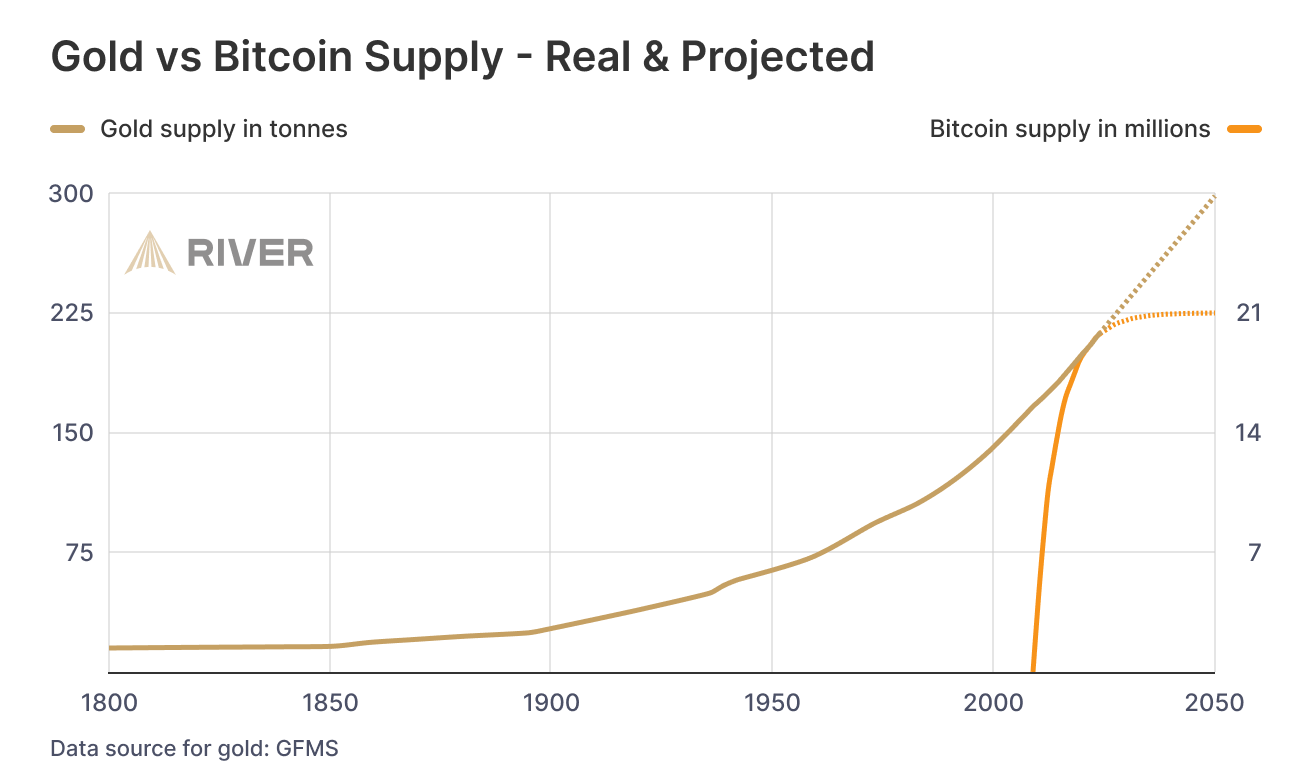
While we argue — fiat erodes every day.
No matter your view on Bitcoin, just show me one other asset that is simultaneously:
– immune to devaluation by decree\ – impossible to print more of\ – impossible to confiscate by a centralized order\ – impossible to counterfeit\ – and, most importantly — transferable across borders without asking permission from a bank, a state, or a passport
💸 Try sending $10,000 through PayPal from Iran to Paraguay, or Bangladesh to Saint Lucia.\ Good luck. PayPal doesn't even work there.
Now open a laptop, type 12 words — and you have access to your savings anywhere on Earth.
🌍 Bitcoin doesn't ask for permission.\ It works for everyone, everywhere, all the time.
📌 There has never been anything like this before.
Bitcoin is the first asset in history that combines:
– digital nature\ – predictable scarcity\ – absolute portability\ – and immunity from tyranny
💡 As Michael Saylor said:
“Bitcoin is the first money in human history not created by bankers or politicians — but by engineers.”
You can own it with no bank.\ No intermediary.\ No passport.\ No approval.
That’s why Bitcoin isn’t just “internet money” or “crypto” or “digital gold.”\ It may not be perfect — but it’s incorruptible.\ And it’s not going away.\ It’s already here.\ It is the foundation of a new financial reality.
🔒 This is not speculation. This is a peaceful financial revolution.\ 🪙 This is not a stock. It’s money — like the world has never seen.\ ⛓️ This is not a fad. It’s a freedom protocol.
And when even the barber starts asking about Bitcoin — it’s not a bubble.\ It’s a sign that the system is breaking.\ And people are looking for an exit.
For the first time — they have one.
💼 This is not about investing. It’s about the dignity of work.
Imagine a man who cleans toilets at an airport every day.
Not a “prestigious” job.\ But a crucial one.\ Without him — filth, bacteria, disease.
He shows up on time. He works with his hands.
And his money? It devalues. Every day.
He doesn’t work less — often he works more than those in suits.\ But he can afford less and less — because in this system, honest labor loses value each year.
Now imagine he’s paid in Bitcoin.
Not in some “volatile coin,” but in hard money — with a limited supply.\ Money that can’t be printed, reversed, or devalued by central banks.
💡 Then he could:
– Stop rushing to spend, knowing his labor won’t be worth less tomorrow\ – Save for a dream — without fear of inflation eating it away\ – Feel that his time and effort are respected — because they retain value
Bitcoin gives anyone — engineer or janitor — a way out of the game rigged against them.\ A chance to finally build a future where savings are real.
This is economic justice.\ This is digital dignity.
📉 In fiat, you have to spend — or your money melts.\ 📈 In Bitcoin, you choose when to spend — because it’s up to you.
🧠 In a deflationary economy, both saving and spending are healthy:
You don’t scramble to survive — you choose to create.
🎯 That’s true freedom.
When even someone cleaning floors can live without fear —\ and know that their time doesn’t vanish... it turns into value.
-
-
 @ bf47c19e:c3d2573b
2025-05-24 16:13:51
@ bf47c19e:c3d2573b
2025-05-24 16:13:51Originalni tekst na bitcoin-balkan.com.
Pregled sadržaja
- Definisanje novca
- Šta je sredstvo razmene?
- Šta je obračunska jedinica?
- Šta je zaliha vrednosti?
- Zašto su važne funkcije novca?
- Novac Gubi Funkciju: Alhemičar iz Njutonije
- Eksploatacija pomoću Novca: Agri Perle
- Novac Gubi Funkciju 2. Deo: Kejnslandski Bankar
- Da li nas novac danas eksploatiše?
- Šta je novac, i zašto trebate da brinete?
- Efikasnija Ušteda Novca
- Zasluge
- Molim vas da šerujete!
Google izveštava o stalnom povećanju interesa u svetu za pitanje „Šta je novac?“ koji se postavlja iz godine u godinu, od 2004. do 2021., a sa naglim porastom nakon finansijske krize 2008. godine.
I izgleda se da niko nema dobar odgovor za to.
 Godišnji proseci mesečnih interesa za pretragu. 100 predstavlja najveći interes za pretragu tokom čitavog perioda, koji se dogodio u decembru 2019. Podaci sa Google Trends-a.
Godišnji proseci mesečnih interesa za pretragu. 100 predstavlja najveći interes za pretragu tokom čitavog perioda, koji se dogodio u decembru 2019. Podaci sa Google Trends-a.Međutim, odgovaranje na ovo naizgled jednostavno pitanje pomoći će vam da razjasnite ulogu novca u vašem životu. Jednom kada shvatite kako novac funkcioniše, tačno ćete videti i zašto svet danas ludi – i šta učiniti povodom toga. Zato hajde da se udubimo u to.
Na pitanje šta je novac, većina ljudi otvori svoje novčanike i pokaže nekoliko novčanica – “evo, ovo je novac!”
Ali po čemu se ove novčanice razlikuju od stranica vaše omiljene knjige? Pa, naravno, zavod za izradu novčanica te zemlje je odštampao te novčanice iz vašeg novčanika kako bi se oduprla falsifikovanju, i svi ih koriste da bi kupili odredjene stvari.
Međutim, Nemačka Marka imala je sva ova svojstva u prošlosti – ali preduzeća danas ne prihvataju te novčanice. Zapravo, građani Nemačke su početkom dvadesetih godina prošlog veka spaljivali papirne Marke kako bi grejali svoje domove. Marka je imala veću vrednost kao papir za potpalu nego kao novac!

1923. nemačka valuta poznata kao Marka bila je jeftinija od uglja i drveta!
Pa šta to čini novac, novcem?
Ispostavilo se da ovo nije pitanje na koje je lako dati odgovor.
Definisanje novca
Novac nije fizička stvar poput novčanice dolara. Novac je društveni sistem koji koristimo da bismo olakšali trgovinu robom i uslugama. Međutim, tokom istorije fizička monetarna dobra igrala su ključnu ulogu u društvenom sistemu novca, često kao znakovi koji predstavljaju vrednost u monetarnom sistemu. Ovaj sistem ima tri funkcije: 1) Sredstvo Razmene, 2) Obračunsku Jedinicu i 3) Zalihu Vrednosti.
Odakle dolaze ove funkcije, i zašto su one vredne?
Šta je sredstvo razmene?
Sredstvo razmene je neko dobro koje se obično razmenjuje za drugo dobro. Najčešće objašnjenje za to kako su se pojavila sredstva razmene glasi otprilike ovako: Boris ima ječam i želeo bi da kupi ovcu od Marka. Marko ima ovce, ali želi samo piliće. Ana ima piliće, ali ona ne želi ječam ili ovce.
To se naziva problem sticaja potreba: dve strane moraju da žele ono što druga ima da bi mogle da trguju. Ako se želje dve osobe ne podudaraju, oni moraju da pronađu druge ljude sa kojima će trgovati dok svi ne pronađu dobro koje žele.
 Ljudi koji trguju robom i uslugama moraju da imaju potrebe koje se podudaraju.
Ljudi koji trguju robom i uslugama moraju da imaju potrebe koje se podudaraju.Vremenom, veoma je verovatno da će se određena vrsta robe, poput pšenice, pojaviti kao sredstvo razmene jer su je mnogi ljudi želeli. Uzimajući pšenicu kao primer: pšenica je rešila “sticaje potreba” u mnogim zanatima, jer čak i ako onaj koji prima pšenicu a nije želeo da je koristi za sebe, znao je da će je neko drugi želeti.
Ovo nazivamo prodajnost imovine.
Pšenica je dobar primer dobra za prodaju jer svi moraju da jedu, a od pšenice se pravi hleb. Pšenica ima vrednost kao sastojak hleba i kao dobro koje olakšava trgovinu rešavanjem problema „sticaja potreba“.
Razmislite o svojoj želji da dobijete više novčanica u eurima ili drugoj valuti. Ne možete da jedete novčanice da biste preživeli, a i ne bi vam bile od velike koristi ako poželite da ih koristite kao građevinski materijal za vašu kuću. Međutim, znate da sa tim novčanicama možete da kupite hranu i kuću.
Stvarne fizičke novčanice su beskorisne za vas. Novčanice su vam dragocene samo zato što će ih drugi prihvatiti za stvari koje su vama korisne.
Tokom dugog perioda istorije, novac je evoluirao do te mere da monetarno dobro može imati vrednost, a da to dobro ne služi za bilo koju drugu ‘suštinsku’ upotrebu, poput hrane ili energije. Umesto toga, njegova upotreba je zaliha vrednosti i jednostavna zamena za drugu robu u bilo kom trenutku koji poželite.
Šta jedno dobro čini poželjnijim i prodajnijim od drugog dobra?
Deljivost
Definicija: Sposobnost podele dobra na manje količine.
Loš Primer: Dijamante je teško podeliti na manje komade. Za zajednicu od hiljada ljudi koji dnevno izvrše milione transakcija, dijamanti čine loše sredstvo razmene. Previše su retki i nedeljivi da bi se koristili za mnoge transakcije.
Ujednačenost
Definicija: Sličnost pojedinačnih jedinica odredjenog dobra.
Loš Primer: Krave nisu ujednačene – neke su veće, neke manje, neke bolesne, neke zdrave. Sa druge strane, unca čistog zlata je jednolična – jedna unca je potpuno ista kao sledeća. Ovo svojstvo se takođe često naziva zamenljivost.
Prenosivost
Definicija: Lakoća transporta dobra.
Loš Primer: Krava nije baš prenosiva. Zlatnici su prilično prenosivi. Papirne novčanice su još prenošljivije. Knjiga u kojoj se jednostavno beleži vlasništvo nad tim vrednostima (poput Rai kamenog sistema ili digitalnog bankovnog računa) je neverovatno prenosiva, jer nema fizičkog dobra koje treba nositi sa sobom za kupovinu. Postoji samo sistem za evidentiranje vlasništva nad tim vrednostima u nematerijalnom obliku.
Kako dobro postaje sredstvo razmene?
Dobra postaju, i ostaju sredstva razmene zbog svoje univerzalne potražnje, takođe poznate kao njihova prodajnost, čemu pomažu svojstva koja su gore nabrojana.
Mnogo različitih dobara mogu u različitoj meri delovati kao sredstva razmene u ekonomiji. Danas, naša globalna ekonomija koristi valute koje izdaju države, zlato, pa čak i robu poput nafte kao sredstvo razmene.
Šta je obračunska jedinica?
Stvari se komplikuju kada u ekonomiji postoji mnogo robe koja se prodaje. Čak i sa samo 5 dobara, postoji 10 “kurseva razmene” između svake robe kojih svi u ekonomiji moraju da se sete: 1 svinja se menja za 15 pilića, 1 pile se menja za 15 litara mleka, desetak jaja se menja za 15 litara mleka, i tako dalje. Ako ekonomija ima 50 dobara, među njima postoji 1.225 “kurseva razmene”!
Sredstvo za merenje vrednosti
Zamislite obračunsku jedinicu kao sredstvo za merenje vrednosti. Umesto da se sećamo vrednosti svakog dobra u poredjenju sa drugim dobrima, mi samo treba da se setimo vrednosti svakog dobra u poredjenju sa jednim dobrom – obračunskom jedinicom.
Umesto da se setimo 1.225 kurseva razmene kada imamo 50 proizvoda na tržištu, mi treba da zapamtimo samo 50 cena.
Na primer, ne treba da se sećamo da litar mleka vredi 1/15 piletine ili desetak jaja, možemo da se samo setimo da litar mleka košta 1USD.
Poređenje dobara je lakše sa obračunskom jedinicom
Obračunska jedinica takođe olakšava upoređivanje vrednosti i donošenje odluka. Zamislite da pokušavate da kupite par Nike Air Jordan patika kada ih jedan prodavac prodaje za jedno pile, a drugi za 50 klipova kukuruza.
Šta je zaliha vrednosti?
Do sada smo gledali samo primere transakcija koje se odvijaju u određenom trenutku u vremenu.
Međutim, ljudi vrše transakcije tokom vremena – oni štede novac i troše ga kasnije. Da bi odredjeno dobro moglo da funkcioniše pravilno kao monetarno dobro, ono treba da održi vrednost tokom vremena.
Novac koji vremenom dobro drži vrednost daje njegovom imaocu više izbora kada će taj novac da potroši.
To znači da prodajnost dobra uključuje njegovu sposobnost da održi vrednost tokom vremena.
Šta jedno dobro čini boljom zalihom vrednosti od drugog dobra?
Trajnost
Definicija: Sposobnost dobra da vremenom zadrži svoj oblik.
Loš Primer: Jagode čine lošu zalihu vrednosti jer se lako oštete i brzo trunu.
Odluka je daleko lakša ako jedan prodavac naplaćuje 150 USD, a drugi 200 USD – odmah je očigledno koja je bolja ponuda jer su vrednosti izražene u istoj jedinici.
Teške za Proizvodnju
Definicija: Teškoće koje ljudi imaju u proizvodnji veće količine dobra.
Loš Primer: Papirne novčanice predstavljaju lošu zalihu vrednosti jer banke i vlade mogu jeftino da ih naprave.
Sa zlatom je suprotno – u ponudi se nalazi ograničena količina uprkos velikoj potražnji za njim, jednostavno zato što ga je vrlo teško iskopati iz zemlje. Ova ograničena ponuda osigurava da svaka jedinica zlata održi vrednost tokom vremena.
Kako dobra postaju zalihe vrednosti?
Dobro postaje zaliha vrednosti ako se vremenom pokaže trajnim i teškim za proizvodnju.
Samo će vreme pokazati da li je neko dobro zaista trajno i da li ga je teško proizvesti. Zbog toga neki oblici novca su postojali vekovima pre nego što je neko otkrio način da ih proizvede više, i na kraju se to dobro više nije koristilo kao novac.
Ovo je priča o školjkama, Rai kamenju i mnogim drugim oblicima novca tokom istorije.
Zlato je primer dobra koje je hiljadama godina služilo kao dobra zaliha vrednosti. Zlato se ne razgrađuje tokom vremena i još uvek ga je teško proizvesti. Hiljadama godina alhemičari su bezuspešno pokušavali da sintetišu zlato iz jeftinih materijala.
Čak i sa današnjim naprednim rudarskim tehnikama, svake godine svi svetski rudnici zlata zajedno mogu da proizvedu samo 2% od ukupne ponude zlata u prometu.
Teškoće u proizvodnji zlata daju izuzetno visok odnos “zaliha i protoka”: zaliha je broj postojećih jedinica, a protok su nove jedinice stvorene tokom određenog vremenskog perioda. Svake godine se stvori vrlo malo novih jedinica zlata, iako je potražnja za zlatom obično vrlo velika.
Kombinujući ovo sa deljivošću, ujednačenošću i prenosivošću zlata, nije ni čudo što je zlato čovečanstvu služilo kao monetarno dobro tokom poslednjih 5.000 godina. Pošto je zlato teško proizvesti, možemo ga nazvati teškim novcem (hard money).
Kao rezultat toga, svoju vrednost je u velikoj meri zadržao kroz milenijume. Cena većine dobara i usluga u pogledu zlata zapravo se vremenom smanjivala kao rezultat tehnoloških inovacija, koje sve proizvode čine jeftinijim.
Uzmimo na primer cene hrane prema praćenju Kancelarije za hranu i poljoprivredu UN-a: sa obzirom na skokove u poljoprivrednoj tehnologiji tokom poslednjih 60 godina, cene hrane drastično su pale kada se procenjuju u zlatu. To čak i važi uprkos činjenici da obični ljudi retko koriste zlato za kupovinu stvari.
 Cene hrane su padale u pogledu zlata tokom proteklih 60 godina, i mnogo pre toga (FAO Indeks Cena Hrane u Zlatu)
Cene hrane su padale u pogledu zlata tokom proteklih 60 godina, i mnogo pre toga (FAO Indeks Cena Hrane u Zlatu)Zaliha vrednosti omogućava ljudima da uštede novac kako bi mogli da ga ulažu u pokretanje preduzeća i obrazovanje, povećavajući produktivnost društva.
Monetarna dobra koja dobro čuvaju vrednost takođe podstiču dugoročniji pogled na život, ili kratke vremenske preference. Pojedinac može da radi 10 godina, uštedi odredjeno monetarno dobro koje je dobra zaliha vrednosti, i nema potrebe da se plaši da će njegova ušteđevina biti izbrisana krahom tržišta ili povećanjem ponude tog dobra.
Zašto su važne funkcije novca?
Kada neki oblik novca izgubi bilo koju od svojih važnih funkcija kao što su sredstvo razmene, obračunska jedinica i zaliha vrednosti, celokupna ekonomija i društvo mogu da se rastrgnu.
Tokom istorije često vidimo grupe ljudi koje eksploatišu druge iskorišćavajući nesporazume o novcu i važnosti njegovih funkcija.
Sledeće, proći ću kroz istoriju novca, prvo hipotetički da bih ilustrovao poentu, a zatim ću preći na stvarne istorijske primere. Kroz ove primere videćemo štetne efekte na društva u slučajevima kada se izgubi samo jedna od tih ključnih funkcija novca.
Novac Gubi Funkciju: Alhemičar iz Njutonije
Kroz istoriju, mnoga dobra su dolazila i odlazila kao oblici novca. Na žalost, kada se neki oblik novca ukine, ponekad postoji grupa ljudi koja eksploatiše drugi oblik manipulišući tim novcem.
Hajde da pogledamo hipotetičko selo zvano Njutonija da bismo razumeli kako dolazi do ove eksploatacije.
Zelene perle postaju Novac
Tokom stotina godina ribolova u obližnjoj reci, stanovnici Njutonije sakupljali su zelene perle iz vode. Zrnca su mala, lagana, izdržljiva, jednolična i retko se pojavljuju u reci. Ljudi prvo priželjkuju perle zbog svoje lepote. Na kraju, seljani shvataju da svi drugi žele perle – one se vrlo lako mogu prodati. Zrnca uskoro postaju sredstvo razmene i obračunska jedinica u selu: pile je 5 zrna, vreća jabuka 2 zrna, krava 80 zrna.
Ukupna ponuda perli je prilično konstantna i cene se vremenom ne menjaju mnogo. Seoski starešina je uveren da može da se opustiti u poslednjim danima živeći od svoje velike zalihe perli.
Alhemičar stvara više perli
Seoski alhemičar je poželeo da bude bogat čovek, ali nije voleo da vredno radi na tome. Umesto da traži perle u reci ili da prodaje vrednu robu drugim seljanima, on sedeo je u svojoj laboratoriji. Na kraju je otkrio kako da lako stvori stotine perli sa malo peska i vatre.
Seljani koji su tragali za perlama u reci bili su srećni ako bi svaki dan pronašli po 1 zrno. Alhemičar je mogao da proizvede stotine uz malo napora.
Alhemičar troši svoje perle
Budući da je bio prilično zao, alhemičar nije svoj metod pravljenja zrna delio ni sa kim drugim. Stvorio je sebi još više perli i počeo da ih troši za dobra na tržištu u Njutoniji. Tokom sledećih meseci, alhemičar je kupio farmu pilića, nekoliko krava, finu svilu, posteljine i ogromno imanje. On je imao priliku da kupi ova dobra po normalnim cenama na tržištu.
Alhemičarevo trošenje ostavljalo je seljanima mnogo perli, ali malo njihove vredne robe.
Svi seljani su se osećali bogatima – imali su tone perli! Međutim, polako su primetili da i svi ostali takodje imaju tone.
Cene počinju da rastu
Uzgajivač pilića primetio je da sva roba koju je trebalo da kupi na pijaci poskupela. Džak jabuka sada se prodaje za 100 perli – 50 puta više od njihove cene pre nekoliko meseci!
Iako je sada imao hiljade perli, uskoro bi mogao da ostane bez njih zbog ovih cena. Pitao se – da li zaista može sebi da priušti da prodaje svoje piliće za samo 5 perli po komadu? Morao je i on da podigne svoje cene.
Jednostavno rečeno, kao rezultat alhemičarevog trošenja njegovih novostvorenih perli, bilo je previše perli koje su jurile premalo dobara – pa su cene porasle.
Kupci robe bili su spremni da potroše više perli da bi kupili potrebna dobra. Prodavci robe su trebali da naplate više da bi bili sigurni da su zaradili dovoljno da kupe potrebna dobra za sebe.
Budući da su cene svih dobara porasle, možemo reći da se vrednost svake perle smanjila.
Nejednakost bogatstva raste
Seoski starešina, koji je vredno radio da sačuva hiljade perli, sada se našao osiromašenim i gladnim. U međuvremenu, alhemičar je udobno sedeo na svom velikom imanju sa kravama, pilićima i slugama koji su se brinuli za svaki njegov hir.
Alhemičar je efikasno ukrao bogatstvo celog sela, tako što je jeftino proizvodio perle i koristio ih za kupovinu vredne robe.
Ono što je najvažnije, kupio je robu pre nego što je tržište shvatilo da je više perli u opticaju i da ima manje robe, što je dovelo do rasta cena. Ova dodatna proizvodnja perli nije dodala korisnu robu ili usluge selu.
Eksploatacija pomoću Novca: Agri Perle
Nažalost, priča o alhemičaru iz Njutonije nije u potpunosti hipotetička. Ovaj prenos bogatstva kroz stvaranje novca ima istorijske i moderne presedane.
Na primer, afrička plemena su nekada koristila staklene perle, poznate kao “agri perle”, kao sredstvo razmene. U to vreme plemenskim ljudima je bilo veoma teško da prave staklene perle, i one su predstavljale težak novac unutar njihovog plemenskog društva.
Niko nije mogao jeftino da proizvede perle i koristiti ih za kupovinu skupe, vredne robe poput kuća, hrane i odeće.
Sve se promenilo kada su stigli Evropljani, i primetili upotrebu staklenih perli kao novca.
U to vreme, Evropljani su mogli jeftino da stvaraju staklo u velikim količinama. Kao rezultat toga, Evropljani su počeli tajno da uvoze perle i koriste ih za kupovinu dobara, usluga i robova od Afrikanaca.
Vremenom se iz Afrike izvlačila vredna roba i ljudi, dok je plemenima ostajalo mnogo perli i malo robe.
Perle su izgubile veći deo vrednosti zbog inflacije uzrokovane snabdevanjem od strane Evropljana.
Rezultat je bio osiromašenje afričkih plemena i bogaćenje Evropljana, kako to ovde objašnjava monetarni istoričar Bezant Denier.
Dragocena roba je kupljena jeftino proizvedenim monetarnim dobrom.
Profitiranje na proizvodnji novca: Emisiona dobit
Ova priča ilustruje kako se bogatstvo prenosi kada jedna grupa može jeftino da proizvodi monetarno dobro.
Razlika između troškova proizvodnje monetarnog dobra i vrednosti tog monetarnog dobra poznata je kao emisiona dobit, eng. seignorage.
Kada je monetarno dobro mnogo vrednije od troškova proizvodnje, ljudi će proizvesti više od monetarnog dobra da bi uhvatili profit od emisione dobiti.
Na kraju će ova povećana ponuda dovesti do pada vrednosti monetarnog dobra. To je zbog zakona ponude i potražnje: kada se ponuda povećava, cena (poznata i kao vrednost) dobra opada.
Novac Gubi Funkciju 2. Deo: Kejnslandski Bankar
U priči o Njutoniji, alhemičar je otkrio način da se od malo peska jeftino stvori više zelenih perli. To se u stvarnosti odigralo kroz trgovinu između Evropljana i Afrikanaca, pričom o agri perlama. Međutim, ove priče su pomalo zastarele – mi više ne trgujemo robom za perle.
Da bismo nas doveli do modernog doba, hajde da promenimo neka imena u našoj priči:
- Selo Njutonija postaje država koja se zove Kejnsland
- Alhemičar postaje bankar
- Seoski starešina postaje penzioner
- Zelene perle postaju zlato, koje niko ne može jeftinije da stvori – čak ni bankar.
Bankar Menja Papirne Novčanice za Zlato
Kao i u stvarnosti, bankar u ovoj priči nema formulu ili trik da stvori više zlata. Međutim, bankar bezbedno čuva zlato u vlasništvu svakog građanina Kejnslanda. Bankar daje svakom građaninu po jednu potvrdu za svaku uncu zlata koje ima u svom trezoru.
Te potvrde se mogu iskoristiti u bilo koje vreme za stvarno zlato. Papirne potvrde ili novčanice su mnogo pogodnije za plaćanje nego nošenje zlata kroz supermarket.
Građani su srećni – oni imaju prikladno sredstvo plaćanja u vidu bankarevih novčanica, i znaju da niko ne može da ukrade njihovo bogatstvo falsifikujući više zlata.
Građani na kraju počinju da plaćaju u potpunosti papirnim novčanicama, ne trudeći se nikad da zamene svoje novčanice za zlato. Na kraju, novčanice postaju “dobre kao i zlato” – svaka predstavlja fiksnu količinu zlata u bankarevom trezoru.
Ukupno kruži 1.000.000 novčanica, od kojih je svaka otkupljiva za jednu uncu zlata. 1.000.000 unci zlata sedi u bankarevom trezoru. Svaka novčanica je u potpunosti podržana u zlatu.
Starešina koji je sačuvao sve svoje perle u priči o Njutoniji sada je penzioner u Kejnslandu, koji svoje zlato drži u banci i planira da ugodno živi od novčanica koje je dobio zauzvrat.
Hajde da u ovu priču dodamo i novi lik: premijera Kejnslanda. Premijer naplaćuje porez od građana i koristi ga za plaćanje javnih usluga poput policije i vojske. Premijer takođe drži vladino zlato kod bankara.
Bankar Menja Papirne Novčanice za Dug
Premijer želi da osigura da nacionalno zlato ostane na sigurnom, pa banku štiti policijom. Bankar i premijer se zbog toga zbližavaju, pa premijer traži uslugu. Traži od bankara da kreira 200.000 novčanica za premijera, uz obećanje da će mu premijer vratiti za pet godina. Premijeru su novčanice potrebne za finansiranje rata. Građani Kejnslanda borili su se protiv većih poreza zbog finansiranja rata, pa je morao da se obrati bankaru.
Bankar se slaže da izradi novčanice, ali pod jednim uslovom: bankar uzima deo od 10.000 novčanica za sebe. Premijer prihvata posao kojim bankar ’kupuje državni dug’. Sada je u opticaju 1.200.000 novčanica, potpomognutih kombinacijom 1.000.000 unci zlata i ugovorom o dugu sa vladom za 200.000 novčanica.
Premijer troši svoje nove novčanice na bombe kupujući ih od dobavljača iz domaće vojne industrije, a bankar sebi kupuje veliki luksuzni stan.
Dobavljač iz vojne industrije koristi sve nove novčanice koje je dobio od premijera da kupi amonijum nitrat (đubrivo koje se koristi u bombama) za proizvodnju bombi. Sve njegove kupovine povećavaju cenu đubriva za uzgajivače pšenice u Kejnslandu, pa oni podižu cenu pšenice.
Kao uzrok toga, pekar koji kupuje pšenicu treba da podigne cenu svog hleba da bi ostao u poslu. Na taj način cene u Kejnslandu počinju da rastu, baš kao što su to činile u Njutoniji kada su nove perle ušle u opticaj.
Papirne Novčanice Više Ne Predstavljaju Zlato
Penzioner nailazi na finansijski časopis u kojem se pominje premijerov dogovor da se zaduži za finansiranje rata. Obzirom da je mudar, on zna da bombe loše vraćaju ulaganje i sumnja da će premijer ikada da vrati svoj dug.
Ako on ‘podmiri’ svoj dug, to bi ostavilo 1.200.000 novčanica u opticaju sa samo 1.000.000 unci zlata da bi ih podržalo, obezvređujući njegovu ušteđevinu. Već oseća stisak u džepu zbog porasta cena, i on odlučuje da se uputi u lokalnu banku i preda svoje novčanice i zameni ih za zlato, koje niko ne može da napravi u većoj količini.
Kada penzioner stigne u banku, on zatiče i mnoge druge okupljene oko banke. Svi oni se nadaju da će uzeti zlato koje predstavljaju njihove novčanice. Građani Kejnslanda sa pravom se plaše da njihove novčanice gube na vrednosti – oni to već osećaju zbog porasta cena.
Vrata su zaključana, sa obaveštenjem bankara na njima:
Po nalogu premijera, onom koji se plaši za stabilnost ove bankarske institucije, ova banka više neće podržavati konvertibilnost papirnih novčanica u zlato. Hvala vam!
Gomila se razilazi, ostavljena sa jednim izborom: da zadrže svoje novčanice, koje sada vrede manje od 1 unce zlata. Građani sa dovoljno finansijske stabilnosti odlučuju da ulože svoje novčanice u kupovinu akcija banke i kompanija vojne industrije, koje dobro posluju jer mogu da kupuju stvari pre nego što se povećaju tržišne cene.
Mnogi ljudi nisu u mogućnosti da investiraju – oni moraju da gledaju kako njihove zarade stagniraju i kako njihova ušteđevina polako ali sigurno gubi vrednost.
Penzioner, koji se nadao da će živeti od novčanica koje je zaradio tokom svojih 40 radnih godina, sada 40 sati nedeljno provodi iza kase u lokalnoj prodavnici, pitajući se gde je sve pošlo po zlu.
Dug Nikada Nije Otplaćen
Prošlo je nekoliko godina, a premijerov dug prema banci dolazi na naplatu. Budući da je potrošio svih 200.000 novčanica na bombe, koje nemaju baš dobar povraćaj ulaganja, on nema novčanice koje može da vrati banci. Plus, premijer želi da kupi još bombi za svoj rat.
Bankar uverava premijera da je sve u redu. Bankar će napraviti novi ugovor o dugu za 600.000 novčanica, koji bi trebao da stigne na naplatu u narednih 5 godina. Premijer može da iskoristi 200.000 od tih novih 600.000 novčanica da vrati svoj prvobitni dug prema banci, zadrži još 300.000 da kupi još bombi i da 100.000 bankaru da bi mu platio njegove usluge.
To nastavlja da se dešava – svaki put kada dug dospeva na naplatu, bankar stvara više novčanica za vraćanje starijih dugova i daje premijeru još više novca za trošenje. Ovaj ciklus se nastavlja.
Šta se dešava u Kejnslandu?
- Oni koji prvi dobiju nove novčanice, gledaju kako se njihovo bogatstvo povećava
- To uključuje bankara, premijera, vladu i sve one koji mogu da pristupe mogućnostima za investiranje u preduzeća koja prva dobiju nove novčanice (finansijske, vojne itd.).
- Cene roba rastu
- Cene se ne povećavaju ravnomerno – one se povećavaju gde god nove novčanice prvo uđu u ekonomiju i od tog trenutka imaju efekat talasa na tržišta. U našem primeru prvo raste cena amonijum nitrata, zatim cena pšenice, pa cena hleba. A tek na kraju zarade običnih ljudi.
- Štednja i životni standard opšte populacije se smanjuju
- Najviše pate oni koji žive od plate do plate i ne mogu da ulažu. Čak i oni koji su u mogućnosti da investiraju podložni su hirovima tržišta. Mnogi su prisiljeni da prodaju svoje investicije po niskim cenama tokom pada tržišta samo da bi platili svoje dnevne potrebe.
- Razlika u prihodima i bogatstvu između bogatih i siromašnih se povećava
- Bogatstvo opšte populacije se smanjuje, dok se bogatstvo onih koji su blizu mesta gde se troše nove novčanice povećava. Rezultat je disparitet koji se vremenom samo proširuje.
Da li nas novac danas eksploatiše?
Priča o Njutoniji i stvarna priča o agri perlama u Africi deluju pomalo zastarelo. Priča o Kejnslandu, međutim, deluje neobično poznato. U našem svetu cene robe uvek rastu, i vidimo rekordne nivoe nejednakosti u bogatstvu.
U poslednjem odeljku ovog našeg članka Šta je novac, proći ću kroz nastanak bankarstva i korake koji su bili potrebni da se dođe do današnjeg sistema, gde banke i vlade sarađuju u kontroli ekonomije i samog novca.
Šta su banke, i odakle su one došle?
Pojava bankarstva verovatno se dogodila da bi olakšala poljoprivrednu trgovinu i da bi povećala pogodnosti. Iako su se mnoga društva na kraju konvergirala ka upotrebi zlata i srebra kao novca, ovi metali su bili teški i opasni za nošenje kao tovar. Međutim, u mnogim slučajevima ih nije ni trebalo prevoziti. Uzmite ovaj primer:
Grad treba da plati poljoprivrednicima na selu za žito, a poljoprivrednici gradskoj vojsci za zaštitu od varvara. U ovom dogovoru zlato se kreće u oba smera: prema poljoprivrednicima u selu kako bi im se platilo žito, i nazad u grad da bi se platila vojska. Da bi olakšali ove transakcije, preduzetnici su stvorili koncept banke. Banka je zlato čuvala u sigurnom trezoru i izdavala novčanice od papira. Svaka priznanica je predstavljala potvrdu da njen imaoc poseduje određenu količinu zlata u banci. Imaoc novčanice je u svako doba mogao da uzme svoje zlato nazad vraćanjem te novčanice banci.
Korisnici banke mogli su lakše da trguju sa novčanicama od papira, i onaj koji poseduje novčanice mogao je da preuzme njihovo fizičko zlato u bilo kom trenutku. To je te novčanice učinilo “dobrim kao i zlato”.
Banke su izdržavale svoje poslovanje naplaćujući od kupaca naknadu za skladištenje zlata ili pozajmljivanjem dela zlata i zaračunavanjem kamata na njega. Trgovina na ovaj način je mogla da se odvija sa laganim novčanicama od papira umesto sa teškim vrećama zlatnika.
Ovakva praksa sa transakcijama, korišćenjem papirne valute potpomognute monetarnim dobrima, verovatno je započela u Kini u 7. veku.
Na kraju se proširila Evropom 1600-ih, a svoj zalet dobila je u Holandiji sa bankama poput Amsterdamske Wisselbanke. Novčanice Wisselbank-e često su vredele više od zlata koje ih je podržavalo, zbog dodane vrednosti njihovih pogodnosti.
Uspon nacionalnih ‘centralnih banaka’
Tokom vekova, zlato je počelo da se sakuplja u trezorima banaka, jer su ljudi više voleli pogodnosti transakcija sa novčanicama.
Na kraju, nacionalne banke u vlasništvu vlada preuzele su ulogu čuvanja zlata od privatnih banaka koje su započeli preduzetnici.
Nacionalne papirne valute potpomognute zlatnim rezervama u nacionalnim bankama zamenile su novčanice iz privatnih banaka. Sve nacionalne valute bile su jednostavno potvrde za zlato koje se nalazilo u trezoru nacionalne banke.
Ovaj sistem je poznat kao zlatni standard – sve valute su jednostavno predstavljale različite težine zlata.
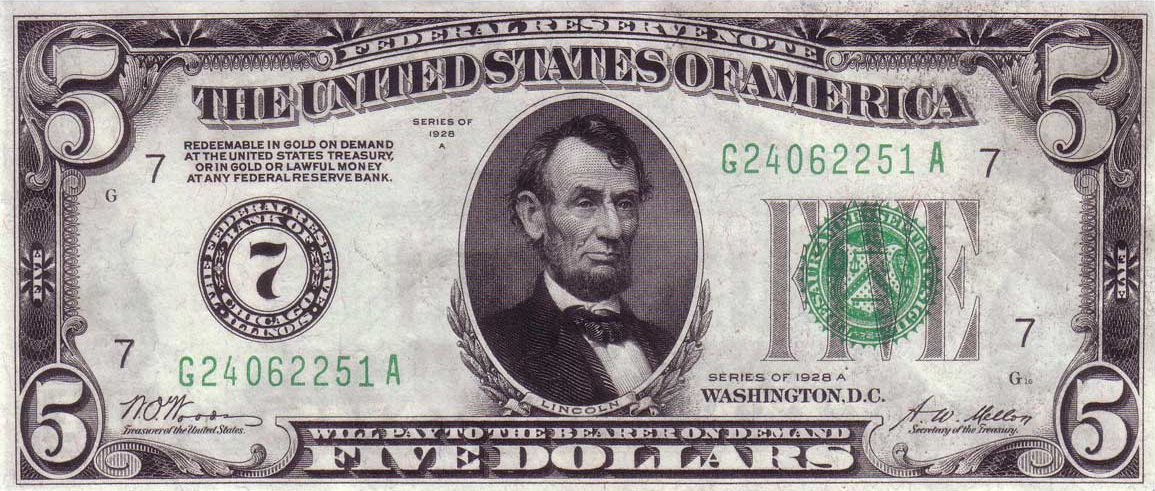 U gornjem levom uglu novčanice možete videti da piše da je novčanica “zamenljiva za zlato”. Savremeni dolari nemaju ovaj natpis, ali inače izgledaju vrlo slično. Izvor
U gornjem levom uglu novčanice možete videti da piše da je novčanica “zamenljiva za zlato”. Savremeni dolari nemaju ovaj natpis, ali inače izgledaju vrlo slično. IzvorZlatni sistem je postojao veći deo vremena, sve do Prvog svetskog rata. Vladama je bilo teško da prikupe novac za ovaj rat putem poreza, pa su morale da budu kreativne.
Kada vlade troše više nego što zarađuju na porezima, to se naziva deficitna potrošnja.
Kako vlade mogu ovo da urade? Vlade to rade tako što pozajmljuju novac prodavajući svoj dug.
Tokom Prvog svetskog rata, vlade su građanima i preduzećima prodavale vrstu duga koja se naziva ratna obveznica. Kada građanin kupi ratnu obveznicu, on preda svoj novac vladi i dobije papir u kojem je stajalo vladino obećanje da će vlasniku obveznice vratiti novac, plus kamate, za nekoliko godina.
Plakat koji obaveštava građane, tražeći od njih da kupe ratne obveznice – što predstavlja zajam vladi. Izvor
Centralne banke ‘monetizuju’ državni dug
Međutim, građani i preduzeća nisu bili voljni da kupe dovoljno ratnih obveznica za finansiranje Prvog svetskog rata.
Vlade se nisu predale – pa su zatražile od svojih nacionalnih ‘centralnih banaka’ da one kupe ove obveznice. Centralne banke su otkupile obveznice, ali ih nisu platile valutom potpomognutom postojećim zlatnim rezervama, kao što su to činili građani i banke prilikom kupovine obveznica.
Centralne banke su umesto toga davale vladi novu, sveže štampanu papirnu valutu potpomognutu samo obveznicom. Ovu valutu podržalo je samo obećanje da će im vlada vratiti dugove. Ovo je poznato kao monetizacija duga.
Budući da su ratne obveznice i valuta samo komadi papira, one su lake i jeftine za proizvodnju i mogu se napraviti u ogromnim količinama. Ono što ograničava proizvodnju i jednog i drugog je poverenje.
Ima smisla da se neko rastane od svog teško stečenog novca da kupi državnu obveznicu, samo ako veruje da će vlada da vrati svoj dug, plus kamate. Centralna banka je “krajnji kupac”, što znači da će ona da kupi državne obveznice kada to niko drugi neće da uradi.
Zapamtite, centralnu banku gotovo da ništa ne košta da kupi državne obveznice, jer oni sami štampaju valutu da bi ih kupili.
Zamislite da pridjete najskupljem automobilu u autosalonu – koji košta 100.000 USD. Mislite da je automobil lep, ali taj novac biste radije potrošili na lepši stan – tako da ste spremni da platite samo 40.000 USD za taj auto.
Sada, hajde da zamislimo da imate štampač za novac i da vas košta samo 50 USD za mastilo i papir da bi ištampali 1.000.000 USD. Vi biste odmah kupili auto, čak i ako biste morali da se cenkate sa drugim čovekom, i da ga na kraju platite 150.000 USD!
Ista stvar se dešava kada centralna banka kupuje obveznice (dugove) od vlade. Centralna banka može da stvori valutu toliko jeftino, da su spremni da plate i više nego što bi drugi platili ove obveznice i nastaviće da ih kupuju čak i kada niko drugi ne bude želeo.
Monetizacija duga uzrokuje inflaciju
Kada centralne banke monetizuju državni dug, funkcija novca kao zalihe vrednosti počinje da se nagriza. Vlada troši novi novac koji je dobila od svoje centralne banke na ratnu robu, obroke i još mnogo toga.
Cene roba rastu od ove novoštampane valute koja kruži kroz ekonomiju. Kada se cene povećavaju, to znači da se vrednost svake jedinice valute smanjuje. Svi koji drže valutu sada imaju manje vrednosti. Danas to nazivamo sporim gubitkom funkcije zalihe vrednosti u novčanoj inflaciji.
Za Nemačku nakon Prvog svetskog rata monetizacija duga izazvala je totalni slom Nemačke ekonomije i stvorila uslove za rast fašizma.
Kao deo sporazuma o prekidu vatre koji je okončao Prvi svetski rat, Nemačka je pobednicima morala da plati ogroman novac. Nemačkoj vladi je bio preko potreban novac, pa su prodale obveznice (dug) Rajhsbanci, nemačkoj centralnoj banci.
Ovaj postupak doveo je do toga da je vlada štampala toliko maraka (tadašnja nemačka valuta) da je tempo inflacije u Nemačkoj ubrzan u hiperinflaciju početkom 1920-ih. Cena vekne hleba za samo 4 godine popela se sa 1,2 marke na 428 biliona maraka.
Tokom i posle Prvog svetskog rata, SAD, Britanija, Francuska i mnoge druge vlade pratile su Nemačku u štampanju valute potpomognute državnim dugom.
To je dovelo do toga da su građani želeli da svoju papirnu valutu zamene za zlato, baš kao i penzioner iz priče o Kejnslandu.
Međutim, mnoge vlade su suspendovale konvertibilnost svojih valuta u zlato. Ovim potezom vlade su primorale svoje građane da drže nacionalnu papirnu valutu i gledaju kako se njihova ušteda smanjuje u vrednosti.
Da bi mogle da nastave da štampaju novac i da bi ga trošile na nepopularne programe za koje nisu mogle da skupljaju poreze za finansiranje – poput ratova.
Bretton Woods: Novi monetarni sistem
Nakon razaranja koja su donela dva svetska rata, vlade su uspostavile novi globalni monetarni sistem prema Bretton Woods-ovom sporazumu iz 1944. godine.
Prema ovom sporazumu, valuta svake države konvertovala se po fiksnom kursu sa američkim dolarom. Američki dolar je zauzvrat predstavljao zlato po stopi od 35 USD za jednu trojsku uncu zlata*.
Sve globalne valute su stoga još uvek bile jednostavna reprezentacija zlata, putem američkih dolara kao posrednika. Redovni građani više nisu mogli da otkupljuju svoje valute za zlato iz Sjedinjenih Država. Međutim, strane centralne banke mogle bi da dođu u Sjedinjene Države da bi zamenile dolare za zlato po stopi od 35 USD za jednu uncu zlata.
Međutim, vlada Sjedinjenih Država nije uvek držala dovoljno zlata da podrži sve dolare u opticaju. Američka vlada nastavila je da finansira proširene socijalne i vojne programe prodajom državnog duga svojoj centralnoj banci, Federalnim rezervama, koja je povećala ponudu dolara bez povećanja ponude zlata koja podupire te dolare.
*Trojna unca je standardna mera čistog zlata i ima malo veću težinu od normalne unce.
Propast Bretton Woods-a
Tokom 1970-ih, sve veći troškovi rata u Vijetnamu i stranih vlada koje su otkupljivale svoje dolare za zlato, stvorili su pritisak na Trezor Sjedinjenih Država.
Ponuda dolara je porasla, dok je zlato u posedu Sjedinjenih Država opalo. Od 1950. pa do početka 1970-ih, rezerve zlata koje je držala vlada Sjedinjenih Država smanjile su se za više od 50%, sa 20 metričkih tona na samo 8 metričkih tona.
Godine 1970. država je imala zlata u vrednosti od samo 12 biliona dolara po zvaničnom kursu od 35 dolara za trojsku uncu zlata. Tokom ovog istog vremenskog perioda, ukupna ponuda američkih dolara otišla je sa oko 32 biliona USD na skoro 70 biliona USD.

Zvanične rezerve zlata u SAD-u su naglo padale od 1950. do 1970. godine, dok su se dolari u opticaju povećavali. Izvor: Wikipedia, DollarDaze.org
Američka vlada nije bila u stanju da potkrepi dolare zlatom od 35 dolara po trojnoj unci, što dovelo do rizika za čitav globalni monetarni sistem.
Početkom sedamdesetih godina, trojna unca zlata trebala je da vredi 200 USD da bi u potpunosti podržala sve američke dolare u opticaju. Rečeno na drugi način, Sjedinjene Države su pokušavale da kažu svetu da jedan dolar vredi 1/35 trojne unce zlata, ali u stvarnosti dolar je vredeo samo 1/200 trojne unce.
Kad su strane vlade trebale da pribave dolare za međunarodnu trgovinu i rezerve, bile su opelješene. Francuska vlada je to shvatila šezdesetih godina prošlog veka i počela je da prodaje svoje američke dolare za zlato po zvaničnom kursu od 35 dolara za trojsku uncu zlata.
Zemlje su počinjale da se bude iz šeme američke vlade. SAD su krale bogatstvo putem emisione dobiti, prodajući dolare za 1/35 trojne unce zlata, kada su vredeli samo 1/200 trojske unce.
Nixonov Šok ulazi u ’tradicionalni’ novac
Da bi kuća od karata mogla da ostane na mestu, predsednik Nixon je 1971. najavio da će američka vlada privremeno da obustavi konvertibilnost dolara u zlato.
Strane vlade više nisu mogle da polažu pravo na zlato svojim papirnim dolarima, a dolar više nije bio “poduprt” zlatom. Nixon je tvrdio da će ovo stabilizovati dolar.
50 godina kasnije, kristalno je jasno da je ovo samo pomoglo dolaru da izgubi vrednost i da ovaj “privremeni” program još uvek traje.
Pre 1971. godine, sve globalne valute bile su vezane za američki dolar putem Bretton Woods-ovog sporazuma. Kada je Nixon promenio američki dolar iz dolara podržanog u zlatu u dolar podržan dugom, ovim je promenio i svaku drugu valutu na Zemlji.
Sam je učinio da se celokupna svetska ekonomija zasniva na dugovima. Valute više nisu predstavljale zlato, već su predstavljale vrednost državnog duga.
Zlatni Standard se nikada nije vratio
Konvertibilnost američkih dolara u zlato – zlatni standard – nikada se nije vratio.
Od 1971. godine, čitav globalni monetarni sistem pokreće se tradicionalnim “fiat” valutama: poverenjem u vladine institucije da održavaju valutni sistem.
Većina valuta podržana je kombinacijom duga njihove vlade i drugih tradicionalnih valuta poput dolara i evra. Papirne valute više nisu podržane zlatom, imovinom koja je više od 5000 godina služila kao težak novac.
Danas vas vlade prisiljavaju da plaćate porez u njihovoj valuti i manipulišu saznanjima oko novca kako bi osigurale da potražnja za njihovom valutom ostane velika.
To im omogućava da neprestano štampaju više valuta, da bi je potrošili na vladine projekte, uzrokujući inflaciju cena koja jede i smanjuje bogatstvo i plate.
Američka vlada sada prodaje državne obveznice (dugove), poznate kao obveznice Trezora SAD, eng. US Treasuries, komercijalnim bankama u zamenu za američke dolare.
Vlada koristi te dolare za finansiranje svog budžetskog deficita. Komercijalne banke prodaju mnoge obveznice Trezora SAD, koje su kupile, američkoj centralnoj banci, Federalnim Rezervama.
Federalne rezerve plaćaju komercijalnim bankama sveže štampanim novcem “pomoću računara i upisivanjem količine na račun”, kako je rekao bivši predsednik Fed-a Ben Bernanke.
Ove komercijalne banke često zarađuju samo kupujući obveznice Trezora SAD od države i prodajući ih centralnoj banci. Kupujte nisko, prodajte visoko.
Centralne banke ovaj proces kupovine državnog duga – odnosno pozajmljivanja novca državi – nazivaju operacijama otvorenog tržišta.
Kada centralna banka odjednom kupi velike iznose duga, oni to nazivaju kvantitativnim ublažavanjem. Centralne banke javno najavljuju kupovinu državnog duga, ali vrlo malo ljudi razume šta to zapravo znači.
Euro, jen i svaka druga valuta koja se danas koristi funkcionišu slično kao američki dolar.
Da li će SAD ikada vratiti svoj nacionalni dug? Neobična stvar u vezi sa državnim dugom SAD-a je ta što vlada poseduje štampariju potrebnu za njegovu otplatu.
Kao rezultat toga, kada vlada duguje novac, oni samo pozajme još više novca da bi otplatile taj dug, povećavajući nacionalni dug.
Ako vam ovo zvuči kao Ponzijeva piramidalna šema, to je zato što ona to i jeste – najveća Ponzijeva šema u istoriji. Kao i svaka Ponzijeva šema, nastaviće se sve dok su ljudi koji kupuju Ponzijevu šemu budu uvereni da će im biti plaćeno nazad.
Ako ljudi i nacije prestanu da se zadužuju i koriste američke dolare jer nemaju poverenja u američku vladu ili vide da cena robe raste (tj. dolar postaje sve manje vredan), potražnja za dolarom će opadati, što će izazvati začaranu spiralu.
Ova spirala često završi u hiperinflaciji, kao što smo videli u novijoj istoriji sa Jugoslavijom, Venecuelom, Argentinom, Zimbabveom i mnogim drugim državama.
Ovo je način kako funkcioniše novac na vašem bankovnom računu. Novac svake nacije na svetu pati od istih problema kao i perle i novčanice u pričama o Njutoniji i Kejnslandu.
Kako banke i vlade kradu tvoj novac?
Tokom vekova, stigli smo do monetarnog sistema u kojem banke i vlade mogu da štampaju novu valutu za finansiranje svojih operacija i svojih prijatelja u zločinu, dok kradu bogatstvo svojih građana.
Šta će se desiti sa svetom kada novac bude mogao da štampa svaki narod na planeti?
- Bogatstvo onih koji su blizu pravljenja nove valute se povećava
- Vlada i politički povlašćena klasa ljudi, imaju pristup novoštampanom novcu pre svih ostalih, pa mogu da ga potroše pre nego što cene porastu. Na ovaj efekat pokazao je ekonomista Richard Cantillon sredinom 1700-ih i poznat je kao Cantillonov Efekat.
- Cena robe raste (poznato kao inflacija
- Ne raste sve roba istovremeno u ceni. Roba blizu mesta gde se proizvodi nova valuta – finansijski sektor i vlada – prva raste, i odatle uzrokuje efekt talasa na cene.
- Inflacija se često predstavlja kao promena cene potrošačke korpe, poznata kao Indeks Potrošačkih Cena, eng. Consumer Price Index (CPI). Vlada ima alate za manipulisanje ovim brojem kako bi osigurala da se ona čini niskom i stabilnom, kao što je objašnjeno u našem članku o inflaciji.
- Finansijska imovina često primećuje ogromnu inflaciju, ali bankari to ne nazivaju inflacijom – oni kažu da naša ekonomija cveta! Nakon što su američke Federalne rezerve učetvorostručile ponudu američkih dolara u šest godina nakon finansijske krize 2008. godine, banke koje su dobile te nove dolare, kupile su akcije i obveznice, stvarajući ogroman balon u cenama ove imovine.
- Štednja i životni standard stanovništva se smanjuju
- Plate su jedna od poslednjih “cena” u ekonomiji koja se prilagođava, jer se često povećavaju samo jednom godišnje. U međuvremenu, cene dnevnih potrepština te osobe koja zaradjuje platu neprestano rastu kako novi novac kruži ekonomijom.
- Najviše su pogođeni oni koji žive od plate do plate – a to je 70% Amerikanaca.
- Razlike u prihodima između bogatih i siromašnih se povećavaju, kao što se vidi na grafikonu ispod.

*Koncentracija dohotka na vrhu naglo je porasla od 1970-ih
Zašto i dalje imamo isti monetarni sistem?
Ako ovaj sistem bogate još više obogaćuje, a siromašne još više osiromašuje, dovodeći do političke nestabilnosti, zašto ga onda ne bismo promenili?
Najveći razlog zašto se ništa ne menja je verovatno to što puno toga ne znamo o samom sistemu. Svi svakodnevno koristimo valute svojih vlada, ali većina nas ne razume kako sistem funkcioniše i šta on čini našim društvima.
Obrazovni sistem, mediji i finansijski stručnjaci neprestano nam govore da je monetarni sistem previše komplikovan da bi ga normalni ljudi razumeli. Mnogi od nas se zato i ne trude da pokušaju.
Još nekoliko razloga zašto ovaj sistem nastavlja da opstaje:
- Mnogo je ljudi koji imaju direktnu korist od štampanja novog novca.
- Ti ljudi ne žele nikakve promene i bore se da zadrže tu moć.
- Nacionalne valute su često pogodne
- Kreditne kartice, online bankarstvo i još mnogo toga čine upravljanje nacionalnim valutama i njihovo trošenje lakim i jednostavnim.
- Građani moraju da plaćaju porez u svojoj nacionalnoj valuti
- To stvara potražnju za tom valutom od svih građana, povećavajući njenu vrednost.
- Glavna međunarodna tržišta, poput nafte, denominirana su u dolarima.
- Nafta je potrebna svakoj zemlji na planeti, ali pošto mnogi ne mogu da je proizvode, moraju da je kupuju na međunarodnim berzama. Od 1970-ih na ovim berzama gotovo sva nafta se prodaje za dolare, što stvara potražnju za dolarima. Da bi se odmaknule od ovog sistema, zemlje bi trebale da pronađu novu valutu ili robu za trgovinu naftom, što zahteva vreme i rizike.
- Nije postojala dobra alternativa
- Uz globalnu ekonomiju u realnom vremenu, naš sistem digitalnog bankarstva koji koristi nacionalne valute je pogodan. Transakcija u tvrdom novcu poput zlata bila bi previše nezgrapna za današnji svet. Digitalna valuta pod nazivom Bitcoin, predstavljena 2009. godine, je rastuća alternativa koja nudi čvrst novac koji se kreće brzinom interneta.
Šta je novac, i zašto trebate da brinete?
Novac je alat koji olakšava razmenu dobara. Kao i svako drugo dobro, novac se pridržava zakona ponude i potražnje – povećanje potražnje povećaće njegovu vrednost, a povećanje ponude smanjiće njegovu vrednost.
Na ovaj način novac se ne razlikuje od kuće ili piletine. Međutim, velika prodajnost novca znači da je potražnja za njim uvek velika. Kao rezultat, novac mora biti težak za proizvodnju (a samim tim i ograničen u ponudi) ili će ga onaj ko ga može napraviti, stvoriti toliko, da vremenom više neće služiti kao zaliha vrednosti. Uskoro će izgubiti svoje funkcije kao sredstvo razmene i obračunske jedinice.
Najbolji novac u datoj ekonomiji je onaj koji se najslobodnije kreće – svi ga žele, lako je obaviti transakcije sa njim i koji sa vremenom dobro drži svoju vrednost. Nijedan novac nije savršen u svemu ovome, a neki ističu jednu funkciju novca na štetu drugih.
Iako se istorija ne ponavlja, ona se rimuje, a usponi i padovi monetarnih sistema imaju jasne ritmove. Uspon i pad monetarnog sistema često sledi opšti obrazac koji smo videli u pričama o agri perlama i Kejnslandu: pojavljuje se odredjenji oblik novca koji pomaže ljudima da efikasnije trguju i štede, ali na kraju gubi na vrednosti kada neko shvati kako da ga jeftino stvori u velikoj količini. Međutim, tokom dugog perioda vremena, monetarni sistemi su se poboljšali u sve tri funkcije novca.
Na primer, zlato je tokom vremena dobro služilo kao zaliha vrednosti. Međutim, naša međusobno povezana ekonomija ne bi mogla efikasno da funkcioniše ako bi trebalo da fizičko zlato zamenimo robom i uslugama. Mnogo je lakše kretati se na papirnom i digitalnom novcu, ali istorija nam govori da su vlade i bankari iskoristili ove oblike novca za krađu bogatstva putem inflacije.
Današnji globalni monetarni sistem je vrlo zgodan, a digitalna plaćanja i kreditne kartice olakšavaju trošenje novca. Ovo skriva stalnu inflaciju koja nagriza vrednost svake jedinice novca i dovodi do sve većeg jaza u bogatstvu.
Nadam se da je ovaj članak proširio vaše razumevanje novca i njegove uloge u društvu. Ovo je samo početak svega što treba istražiti o novcu: za kasnije su sačuvane teme o inflaciji, kamatnim stopama, pozajmljivanju, poslovnim ciklusima i još mnogo toga.
Efikasnija Ušteda Novca
Možda se pitate kako zaštititi svoju štednju kada svaki oblik često korišćenog novca i investicija pati od inflacije ponude – koja umanjuje vrednost i prenosi bogatstvo onima koji mogu da stvore novac ili investiciju. Možda se čini da se ništa na planeti danas ne može kvalifikovati kao ‘težak’ novac, ali dve stvari ipak ostaju: zlato i njegov noviji rođak Bitcoin. Obe ove stvari je neverovatno teško proizvesti, a jedna od njih se kreće brzinom interneta i može se čuvati u vašem mozgu.
Ako želite da saznate više o Bitcoin-u kao sredstvu za zaštitu vaše ušteđevine, pročitajte ovde. Ako ste već spremni za kupovinu Bitcoin-a, pogledajte moj vodič za kupovinu Bitcoin-a. Možete početi sa investiranjem sa samo 5 ili 10 €.

Zasluge
Hvala svima koji su pomogli u izradi i uređivanju ove serije o novcu: @ck_SNARKS, @CryptoRothbard, Neil Woodfine, Emil Sandstedt, Taylor Pearson, Parker Lewis, Jason Choi, mojoj porodici i mnogim drugima.
Hvala svima koji su ovo inspirisali i razvili ključne ideje koje su ovde primenjene: Friedrich Hayek, Carl Menger, Ludwig Von Mises, Murray Rothbard, Saifedean Ammous, Dan Held, Pierre Rochard, Stephan Livera, Michael Goldstein, i mnogi drugi.
Molim vas da šerujete! Ako vam je ovaj članak otvorio oči o tome kako funkcioniše naš novac i finansijski sistem, kontaktirajte me ili ostavite komentar!
Ako vam se sviđa moj rad, molim vas da ga podelite sa svojim prijateljima i porodicom. Cilj mi je da svima pružim pogled u ekonomiju i na to kako ona utiče na njihov život.
-
 @ f7d424b5:618c51e8
2025-05-18 18:03:25
@ f7d424b5:618c51e8
2025-05-18 18:03:25GAMERS, Join us for a vicless episode where we talk about AI for a change and how it has been impacting our lives. I promise it's video games related.
Stuff cited:
Obligatory:
- Listen to the new episode here!
- Discuss this episode on OUR NEW FORUM
- Get the RSS and Subscribe (this is a new feed URL, but the old one redirects here too!)
- Get a modern podcast app to use that RSS feed on at newpodcastapps.com
- Or listen to the show on the forum using the embedded Podverse player!
- Send your complaints here
Reminder that this is a Value4Value podcast so any support you can give us via a modern podcasting app is greatly appreciated and we will never bow to corporate sponsors!
-
 @ 7460b7fd:4fc4e74b
2025-05-18 11:02:09
@ 7460b7fd:4fc4e74b
2025-05-18 11:02:09比特币持有者在 iPhone 上的安全使用注意事项
引言:iPhone 与安卓的对比
当涉及移动设备安全,比特币持有者面临着在 iPhone 和安卓设备之间的选择。从安全硬件来看,安卓阵营中确有一些型号配备了类似于 Apple Secure Enclave 的硬件安全模块,例如 Google Pixel 手机内置的 Titan M/M2 安全芯片,用于保障启动流程和存储敏感数据us.norton.com;三星的旗舰机型则集成了 Samsung Knox 多层安全平台,经过多国政府机构认证,可在硬件层面保护设备及其中数据us.norton.com。这些安全措施大大提升了设备抵御恶意攻击和数据泄露的能力。然而,需要注意的是:具备此类高级安全特性的安卓机型在市场上相对少见,并非安卓阵营的普遍标准us.norton.com。安卓生态高度碎片化,不同厂商的安全实践差异悬殊;除了少数注重安全的厂商(如 Google、Samsung)外,许多设备缺乏统一的安全保障水平us.norton.com。尤其在二手市场上,安卓设备型号繁杂且来源不一,一些旧款或改装机型可能缺少最新的安全芯片或更新,使安全性难以得到保证。
相比之下,Apple iPhone 全系列自带硬件级的安全隔区(Secure Enclave),统一的闭源系统和严格的应用审核使其安全措施在所有设备上保持一致us.norton.com。同时,iPhone 引入的 Face ID(三维结构光人脸识别)在生物识别安全性上具有独特优势。Apple官方数据显示,Face ID 被他人解锁的概率只有 百万分之一,远低于指纹识别的五万分之一。这源于Face ID利用红外点阵投射捕捉面部3D结构,难以被照片或面具所破解,大幅减少了伪造生物特征解锁的风险。此外,相较许多安卓手机仍依赖的二维人脸识别或电容/光学指纹,Face ID 在抗攻击能力上更胜一筹——例如普通指纹残留可能被提取复制,而二维人脸解锁曾被照片轻易骗过,但Face ID的深度感应技术有效避免了这些漏洞。
综上所述,在移动设备安全领域,iPhone 为比特币等高价值敏感资产的持有者提供了更为稳健和统一的安全基础。尽管某些高端安卓手机具有可圈可点的安全功能,但鉴于这类机型凤毛麟角、安卓设备更新和管控的不统一,以及生物识别方案的差异,我们强烈建议将 iPhone 作为比特币手持设备的唯一选择。从硬件加密到生物识别,iPhone 的封闭生态和领先技术能为数字资产提供更可靠的防护,而安卓设备在这一场景下则存在诸多先天不足。
小结: 安卓阵营虽有Pixel Titan芯片、Samsung Knox等亮点,但安全机型数量有限且良莠不齐;iPhone凭借统一的安全架构和先进的Face ID,在保护敏感数据方面更胜一筹。为确保比特币等资产安全,选择安全可靠的iPhone 是明智之举。
iPhone 安全配置指南
选择了 iPhone 作为比特币存取和通讯设备后,仍需进行细致的安全设置,以最大化利用其安全潜力。以下是针对比特币持有者的 iPhone 安全配置要点:
-
禁用 Face ID/Touch ID 生物解锁,改用强PIN码: 建议关闭面容ID解锁功能,改用6位以上的数字PIN码(或更复杂的字母数字密码)作为解锁方式。在紧急情况下,生物识别容易被他人强制利用(例如他人将手机对准机主面部强行解锁),而记忆型的PIN码只有持有人知晓,更难以被胁迫获取。此外,法律上某些地区对强制提供生物特征和提供密码有所区别,这也使得使用PIN码在极端情况下更有保障。
-
启用自动锁定(1分钟) 将设备设为闲置1分钟后自动锁定屏幕。从安全角度出发,锁定等待时间越短越好。1分钟的设置可确保即使暂时离开或疏忽,设备也会很快上锁,防范他人乘虚而入。养成随手锁屏的习惯固然重要,但有了短自动锁定时间作为双重保障,安全性更上一层楼。
-
开启输错10次自动抹除: 在“设置 > 面容ID/触控ID与密码”中启用“连续输错10次密码抹掉数据”功能。一旦有人反复尝试猜测密码,该功能会在第十次错误尝试后自动抹除手机数据。很多用户担心该设置存在风险,但事实上 误触发的可能性极低。sspai.comsspai.com实际测试表明,iPhone在多次输错密码时会触发累进的延迟惩罚机制:第五次错误需要等待1分钟,第六次错误等待5分钟,第7-8次各等待15分钟,第9次等待1小时sspai.comsspai.com。要连续进行十次独立的错误尝试至少需要约96分钟,在现实中“熊孩子”乱按连续清空数据几乎不可能发生sspai.com。相反,该功能对抗暴力破解极为有效——正如2015年圣贝纳迪诺恐怖袭击案中,嫌犯所用的iPhone就启用了十次错误清除,使FBI也无法轻易尝试破解en.wikipedia.org。总之,此项设置能将设备落入他人之手时的数据泄露风险降至最低。
-
利用应用级 Face ID 控制(iOS 18+):升级至iOS 18或更新版本,充分利用其新增的应用锁定功能。长按主屏某个应用图标,可以找到“需要Face ID”选项,将该应用加锁theverge.com。被加锁的应用每次打开都需要通过Face ID身份验证(即使手机已解锁)。建议对 聊天通讯、密码管理、交易所App 等敏感应用启用此功能。例如,将微信、Signal、邮件客户端等设置为打开需Face ID验证,以防范他人在您手机解锁的短暂间隙内获取其中内容。应用级Face ID锁定为设备提供了第二道防线:即使手机本身已解锁,敏感应用和数据仍受到保护。
-
建议购买第二台 iPhone 或 iPad 作为“备用解锁入口”: 利用 Apple 的“信任链”机制,为同一 Apple ID 配置多台受信任设备(如两台 iPhone 或 iPhone+iPad)。这样即使主设备丢失或被抹除,备用设备依然可以访问并恢复 iCloud 端到端加密数据。其安全本质类似于“1-of-N 多签”,即任一设备均可独立解锁所有云数据,但无需多设备联合协商,恢复更灵活。注意:这与比特币的m-of-n多签不同,Apple的信任链是单设备多入口,安全性和便利性权衡需根据个人需求评估。官方说明参见:Apple平台安全白皮书(Keychain与信任链)
-
建议购买 YubiKey 等硬件安全密钥作为 Apple ID 验证要素: 由于信任链机制下新设备加入时,身份验证成为潜在攻击点(如钓鱼、社工、短信劫持),推荐为 Apple ID 配置 YubiKey 或兼容 FIDO2/U2F 的硬件安全密钥。启用后,只有插入并触发硬件密钥的情况下,才能完成新设备授权、敏感操作或账户恢复,有效阻止网络钓鱼和大部分远程攻击。该方法可显著提升账户安全,降低因凭证泄漏或验证被劫持导致的信任链攻破风险。Apple 官方说明:为 Apple ID 添加安全密钥
通过上述配置,iPhone 将处于一个平衡了便利性和安全性的状态:日常解锁采用PIN码确保意外情况下设备不被强制解锁,短自动锁和十次清除严防暴力破解,而应用级加锁进一步保障重要数据不外泄。
小结: 按照以上指南对iPhone进行安全配置,可以大幅提升设备在实际使用中的抗攻击能力。生物识别解锁的取舍、自动锁定和清除机制、以及iOS 18引入的应用加锁功能相结合,全方位地巩固了手机作为比特币手持设备的安全基石。
关于自动抹除的常见质疑回应
启用“输错10次自动抹除”功能后,不少用户会提出疑虑,主要集中在两个方面:其一,担心儿童误操作或本人一时疏忽导致设备数据被抹掉;其二,担心万一手机数据被抹除,设备本身价值受损。针对这些质疑,我们进行如下回应:
-
“熊孩子乱按怎么办?” 前文已提及,iPhone设计了渐进延时机制,使得连续十次错误输入并非易事sspai.comsspai.com。孩子无意识地反复点击相同数字,系统只视为一次错误sspai.com;而多次不同错误则会触发越来越长的锁定时间,很难真的连续试满十次sspai.com。实践中,要触发十次错误清除需要近两个小时且每次输入都不同,这种情景极不现实sspai.com。因此,只要平时看护好设备,误抹除几乎无需担心。相反,如果没有该功能,一旦设备遗失或被不法分子获取,后果将不堪设想——对方可以在足够时间和专业工具协助下尝试无限次解锁,从而获取您手机中的一切秘密。
-
“数据没了岂不可惜?” 我们强调,比特币持有者手机中存储的敏感信息价值远超设备本身。手机里可能有助记词、私钥线索、交易记录截图,甚至包含您社交账户中关于资产的对话。在攻击者眼中,这些数据的价值胜过一部手机。与其担心设备被误清除,不如担心设备落入他人之手数据遭泄露的风险。况且,对于重要数据您应当早有备份(下文将讨论启用iCloud云备份的问题)。即使真发生误清除,有备份在手也能恢复;但若数据被不法分子窃取,一旦造成资产损失将无法挽回。因此,从风险权衡来看,“宁可误删,不可被盗”——自动抹除是最后一道保障,在极端情况下保护您的数字资产不被侵害。
总而言之,这一功能的利远大于弊。儿童误触可以通过良好监护和系统延时设计来防范,而一旦启用,您将获得巨大的安心:手机若遭试图破解,可以自毁以保全数据安全。这正是比特币持有者应有的安全理念:舍弃设备保安全,数据和资产永远优先于硬件。随着良好备份策略的配合(例如iCloud加密备份),启用自动抹除几乎没有后顾之忧。
小结: 针对自动抹除功能的疑虑更多是误解。iPhone的机制使得误触发几率极低,而其提供的数据安全保障却是无可替代的。比特币等敏感资产持有者应放下顾虑,优先保护数据安全——哪怕代价是设备被清除,也胜过数据落入他人之手。
iCloud 备份的争议与建议
在确保本地设备安全的同时,妥善备份数据同样关键。对于比特币持有者而言,启用 iCloud 云备份可以提供额外的一层安心:万一设备遗失、损坏或被抹除后,仍有机会恢复重要信息。然而,围绕iCloud备份的安全性一直存在争议,我们在此详细分析并给出建议:
首先强烈建议在启用iCloud备份的同时,务必开启「高级数据保护」(Advanced Data Protection, ADP)。默认情况下,iCloud云备份的数据加密密钥由Apple掌管,这意味着苹果公司在法律要求下能够解密并提供您的备份数据support.apple.comsupport.apple.com。而开启高级数据保护后,备份所涉及的大部分数据将采用端对端加密,只有您的受信任设备掌握解锁密钥support.apple.com。据苹果官方说明,在ADP模式下,即便苹果公司也无法读取您的备份内容support.apple.com。因此,高级数据保护能够将使用云备份可能带来的隐私泄露风险降至最低(前提是您妥善保管好自己的账户和恢复密钥)。
启用云备份常见的疑虑是:“会不会把我的钱包私钥也备份上去,万一云被攻破岂不危险?” 实际上,多数主流比特币/加密钱包软件不会将核心密钥(如助记词或扩展公钥xpub)存储在云备份中。很多钱包在设计时就要求用户自行备份助记词,而不会把这些高度敏感的数据写入应用沙盒,可被iCloud备份抓取。同样地,一些钱包应用甚至提醒用户关闭iCloud备份以防助记词泄露support.wallet.coinex.com。换言之,开启iCloud备份并不会将您的私钥上传(除非个别钱包特别设置了云同步,但大多数非托管钱包都没有这么做)。当然,为审慎起见,您可以查阅所用钱包的文档或设置,确认其是否有备份敏感信息到云的选项,并据此做出取舍。
与此同时,我们更加关心的是其他应用的数据完整备份。对于比特币持有者来说,聊天记录、笔记文档和工作应用的数据往往同样敏感且重要。例如,常用通讯软件(微信、Telegram、Signal 等)中的聊天可能涉及交易细节或人脉网络;办公应用如钉钉、飞书则包含财务往来或业务资料。这些应用的数据都会包含在iCloud整机备份中并被完整保存,一旦手机丢失或损坏,可以通过云备份原样恢复。support.apple.com值得一提的是,在高级数据保护开启且不泄漏密钥的前提下,这些备份数据即使存储在苹果服务器上也是安全的,第三方无法解读其中内容。
进一步的好处是:利用备份进行调查取证。假设最坏情况发生——您的手机被抹除或遗失,但是事先有一份最新的iCloud备份。在紧急需要时,您可以在一台新的iPhone上恢复这份备份。在恢复完成后,切断新设备的网络连接(拔掉SIM卡或不连Wi-Fi)。由于备份恢复会还原您的应用登录状态和本地数据,新设备在离线情况下将维持原手机当时的登录环境。您可以打开聊天应用、邮件、照片等查看内容,就像原手机一样。离线操作确保应用不会因为检测到新设备而要求重新登录,也避免了云端数据被远程清除的可能。这对于事后取证、提供线索给执法部门或自我调查都极为有利。比如,若涉及盗窃诈骗案件,这部离线恢复的手机里保留的聊天记录、交易凭证可以作为关键证据。而一旦联网,这些应用可能出于安全考虑登出账户或拉取最新状态,反而不利于保留原始证据。因此,有意识地保存一份完整云备份,并在需要时以离线方式恢复,是一种非常巧妙的应对策略。
小结: 尽管人们对云备份心存疑虑,但通过启用高级数据保护,iCloud备份既能提供数据恢复便利,又充分保障了隐私安全。大多数加密钱包不会上传私钥等核心数据,而聊天、办公等应用的数据则可完整份以备不时之需。在平衡安全与可用性的前提下,开启iCloud备份(搭配ADP加密)是明智之举——它让您在设备意外损坏或丢失时依然有据可查、有据可证。
高级数据保护与密码学机制分析
最后,我们从更宏观的视角,结合真实案例和技术原理,深入探讨苹果设备与云服务的安全性,以及高级数据保护(ADP)所依赖的密码学机制。这部分将涵盖苹果在多个国家遭遇的解锁争议、ADP 的运作及其与实体安全密钥的配合、以及关于苹果是否存在解密后门的分析。
苹果与执法部门的解锁事件
过去数年间,多起高调事件凸显了设备加密与执法取证之间的矛盾。美国国会山骚乱事件(2021年1月6日)中,执法部门缴获了大量嫌疑人的手机。据报道,不少嫌犯使用的是iPhone,调查人员能够从苹果获取其中的数据 但途径主要是通过 iCloud 云备份 而非直接破解设备thedailybeast.com。由于当时高级数据保护尚未推出或未启用,苹果依然持有那些嫌疑人iCloud账户的备份密钥,因此在收到合法的执法请求后,苹果向FBI提供了嫌疑人的iCloud备份内容,其中包括视频、照片和聊天记录等关键证据thedailybeast.com。这些数据帮助当局重构了案件过程,也反映出如果用户没有使用端到端加密备份,云端数据在法律压力下并非牢不可破。
相反,在更早的**圣贝纳迪诺恐怖袭击案(2015)**中,FBI面对一部启用了强加密的嫌犯iPhone却陷入僵局。那是一个运行iOS 9的 iPhone 5C,开启了PIN码锁和10次输错清除功能en.wikipedia.org。由于该设备上的本地数据经过设备加密且苹果并不持有密钥,FBI无法提取其中信息,遂求助苹果公司要求破解。但苹果以维护所有用户安全为由拒绝编写后门固件来绕过安全限制,引发了一场著名的法律拉锯en.wikipedia.orgen.wikipedia.org。最终执法部门辗转通过第三方工具解锁了手机,但苹果的立场十分明确:即便面对恐怖主义案件,也不会为单次事件在系统中留下后门。这一事件凸显出现代iPhone设备本地加密之强大——在没有用户密码的情况下,即使连厂商都无能为力,除非另辟蹊径寻求系统或硬件漏洞。
iCloud 在中国与英国的访问争议
在不同国家,苹果围绕用户数据加密与政府监管的博弈也在上演。中国方面,自2018年以来苹果将中国大陆 iCloud 服务交由“云上贵州”公司运营,数据存储和加密密钥均留在境内zh.amnesty.org。依据中国《网络安全法》,云服务运营者有义务为执法和国家安全机关提供“技术支持和协助”zh.amnesty.org。这意味着若中国警方出于刑侦需要向云上贵州调取某用户的 iCloud 数据,该公司必须配合提供,几乎没有拒绝的空间zh.amnesty.org。更重要的是,苹果把中国用户的 iCloud 加密密钥也存放在中国,一旦收到合法命令要求解密数据,苹果和云上贵州只能遵从zh.amnesty.org。换言之,在标准数据保护模式下,中国当局有途径通过法律手段获取本地存储的iCloud明文数据。这引发了人们对隐私的担忧:如果没有端到端加密,中国的用户数据可能在政府要求下被查看。然而如果用户开启高级数据保护,使得苹果也无法解读备份内容,那么即便在中国,此举从技术上为用户争取到了更高的私密性(前提是中国地区允许开启ADP——截至目前,苹果并未在中国禁用该功能,国区用户依然可以自行启用高级数据保护support.apple.comsupport.apple.com)。
再看英国的情况。英国政府近年以打击犯罪和恐怖主义为由,不断向科技公司施压要求提供加密数据的后门访问权。2023年底,英国援引《调查权力法》(IPA)秘密向苹果发出“技术能力通知”(TCN),要求苹果在全球范围内为英国安全部门提供对加密iCloud内容的解锁途径cnbeta.com.tw。这实际上等同于要求苹果破坏其端到端加密体系,留出一个只有政府能用的后门。苹果对此断然拒绝,并做出强硬回应:宁愿撤除在英服务,也不会妥协安全底线cnbeta.com.tw。结果是,苹果选择在英国境内停止提供高级数据保护功能给新用户。已有启用ADP的英国用户被通知需在宽限期内手动将其关闭,否则将无法继续使用iCloud备份cnbeta.com.tw。苹果在声明中表示对此深感失望,但为了遵守当地法律别无他法cnbeta.com.tw。下面这张截图显示了英国用户在系统中看到的提示信息,明确告知ADP服务不再可用

苹果针对英国地区做出的ADP功能调整通知。英国政府要求能够解密用户数据,迫使苹果撤回了对英国用户的新端到端加密备份支持cnbeta.com.twcnbeta.com.tw。苹果声明强调只有用户本人才能解读其加密数据,并重申不会在产品中留下执法后门cnbeta.com.tw。
这一英国内外的罕见举措表明,各国政府正日益重视加密带来的执法障碍,而苹果则在平衡用户隐私和法律要求之间走钢丝。尽管英国的情况迫使苹果让步(取消当地ADP),但苹果并未真的为政府打造解密后门,而是通过限制功能来表明态度——这与其长期立场一致:绝不在加密产品中留后门,即使承受业务上的损失cnbeta.com.tw。
高级数据保护与安全密钥
高级数据保护(ADP) 是苹果于 iOS 16.2 引入的一项可选功能,其核心是在用户选择开启后,将包括设备备份在内的大部分 iCloud 数据升级为端到端加密存储support.apple.comsupport.apple.com。开启ADP有两个前提:账户已启用双重认证,以及设置了账户恢复联系人或恢复密钥,以防用户遗失访问权限support.apple.comsupport.apple.com。在ADP模式下,Apple不再持有绝大部分云数据的解锁密钥,这些密钥只存在于用户的受信任设备中support.apple.com。这意味着,即便苹果公司收到政府索取数据的要求或其服务器遭黑客攻击,没有密钥的加密数据对任何第三方都是无意义的乱码。正如苹果声明所言:“只有拥有数据的用户才能解密,Apple 无法访问端对端加密的数据”cnbeta.com.tw。可以说,ADP将用户云数据的主导权完全交还给用户自己,从而彻底消除了苹果方面潜在的数据泄露点。
为了进一步增强账户安全,苹果在_iOS 16.3_开始支持绑定实体安全密钥(如 YubiKey)作为 Apple ID 的额外两步验证方式sspai.com。过去Apple ID登录主要依赖密码+发送到受信设备的验证码,但假如用户Apple ID密码泄露,攻击者可能利用社会工程获取验证码。而引入实体安全密钥后,用户可以要求任何新的登录尝试都必须提供物理密钥认证才能完成。这相当于给 Apple ID 上了一把“硬件锁”。对于比特币持有者而言,这一步非常值得配置:即使黑客骗取了您的苹果账号密码,没有您的YubiKey或同类FIDO2安全密钥,他仍无法登录您的iCloud或停用您的ADP。安全密钥本身具有防钓鱼特性,它不会把可被重用的机密泄露给假网站,再加上密钥私藏于硬件内部不可导出,使得账户保护达到新的高度sspai.comsspai.com。简而言之,**“ADP + 硬件安全密钥”**的组合为用户云数据打造了双重护城河:前者确保云上数据加密不被窥探,后者确保账户本身不被劫持利用。
需要注意的是,启用ADP后如果遗失所有设备且忘记密码,苹果无法帮您找回数据support.apple.com。这就像您把保险箱钥匙只握在自己手里而不交给任何人保管,其安全性空前提高,但也意味着责任完全在您。因此请务必牢记Apple ID密码,保管好恢复密钥或紧急联系人。一旦平衡好便利与安全,这套机制将为您的数字资产提供堪比硬件钱包的云端保障。
后门密钥与私钥不可拆分性
现代加密体系的设计使得用户私钥与设备环境密不可分。在苹果的生态中,每台设备都拥有由硬件生成的唯一加密根密钥。例如,安全隔区(Secure Enclave)内嵌入了设备唯一标识符UID作为根密钥,UID由安全硬件随机生成并烧录至芯片中help.apple.com。这个UID既不与任何其他设备标识相关,也无法被设备外的任何人(包括苹果官方)获取help.apple.com。同时,用户的解锁密码与该UID进行数学“交织”(entangle),共同派生出加密密钥help.apple.com。换言之,设备硬件密钥和用户密码共同决定了数据加密密钥,没有这两者就无法还原密钥。这体现了用户私钥对设备及用户身份的强绑定——苹果没有第三方密钥可以绕过这一绑定关系help.apple.comhelp.apple.com。
从密码学角度来看,如果苹果试图在上述体系中插入一个额外的“后门密钥”,将面临巨大的技术困难,并且这样的异常极易被察觉。设想苹果通过异或(XOR)或 Shamir 密钥共享等方式,将一个后门密钥与用户密钥组合:
- 实现层面的异常:用户设备在正常情况下应当能够独立完成解密/签名操作。如果加入隐藏密钥份额,意味着设备单凭用户自己的密钥无法完成某些解密,必须依赖苹果持有的那一份。这样的改动会造成额外的密钥协商步骤或异常的解密失败。例如,若苹果将后门密钥与用户密钥异或生成实际工作密钥,那么单用用户密钥将无法解密出正确结果,设备可能需要静默地向苹果服务器请求密钥片段或进行额外计算。这类非预期的通信或计算步骤很容易被安全研究者通过流量分析或逆向工程发现端倪。再比如采用 Shamir’s Secret Sharing 等门限方案,如果苹果持有一份密钥碎片,设备在解密时就需要满足门限条件,这通常意味着需要苹果的参与或预置公钥,从而在协议日志中留下异常痕迹。任何偏离常规协议的做法——无论是多传输一段数据,还是多保存一段密钥信息——都可能成为研究者捕捉的线索。历史经验表明,密码协议中的“奇怪之处”往往预示潜在漏洞或后门:例如 NSA 推出的 Dual_EC_DRBG 伪随机数生成器由于使用了异常常数,被专家迅速怀疑存在后门;著名密码学家施奈尔(Bruce Schneier)就曾直言 Dual_EC_DRBG 中的后门“相当明显”,呼吁业界停止使用en.wikipedia.org。由此可见,试图暗中插入额外密钥会在数学实现上留下破绽,而资深密码学者和安全社区有足够能力识别这些反常之处。
进一步,从门限签名理论对比苹果现有密钥管理,可以加深这一不可行性的理解。门限密码学允许将密钥拆分给多方持有,只有达到预定门槛的份额才能重构密钥或执行签名解密toc.csail.mit.edumedium.com。其优点在于提高了密钥托管的安全性,需要多方协作才能解锁秘密。然而,这种机制是公开设计的一部分,各参与方和流程都是明示的。例如在某些区块链多重签名方案中,多个私钥持有者共同生成交易签名,每个人都知晓门限机制的存在。相较之下,苹果在产品中的密钥管理要么是完全由用户端掌握密钥(如iPhone本地数据加密,密钥存在Secure Enclave中),要么是在用户许可下由苹果代管(如传统iCloud云备份未启用高级加密时,苹果保存备份密钥)。苹果并没有公开采用“两方门限”的模式来和用户分享密钥,否则等于声明“用户单方无法完全掌控自己的解密权”。如果苹果暗中采用门限签名让自己持有一份密钥碎片,本质上就是一种**变相密钥托管(Escrow)**行为。这样的做法会明显偏离苹果宣称的零后门立场,与其在隐私政策中反复强调的原则相违背。值得注意的是,苹果在其官方隐私声明中明确表示:“我们从未在任何产品或服务中创建过后门或万能解锁主密钥”apple.com。因此,从理论和实践双重层面来看,用户私钥与潜在后门密钥是难以在不被发现的情况下拆分存在的。任何试图将二者解耦的举措都会引起体系架构的异常,进而难逃专家法眼。
加密社区对后门的发现与审计
在当今的安全生态中,不存在“悄无声息的后门”。一旦厂商试图在加密方案中掺入后门密钥,全球的密码学社区和安全研究人员都有多种手段将其揪出。下面从几个方面概述社区常用的后门检测与审计方法:
-
开源协议分析:安全专家偏好开源的软件和协议,因为源码透明意味着任何可疑的算法修改、密钥处理流程都暴露在公众视野中。通过阅读和形式化分析公开的协议规范,研究者可以发现是否有多余的密钥交换步骤或异常的参数。例如,Signal通信协议的源代码和技术细节是完全公开的,全球专家曾多次审阅其实现,验证其端到端加密未存在后门linkedin.com。事实证明,公开透明带来的是更严苛的监督,任何隐秘加入的密钥参数都有可能被审计人员发现。正如业内人士所指出的,Signal 采用开放源码意味着安全专家可以独立审计其代码以核实安全性linkedin.com。类似地,许多现代加密库都会经过社区审视,以确保其中没有“暗门”。
-
逆向工程与二进制审计:对于闭源的软件(例如苹果自身的系统组件),安全研究者会运用逆向工程技术来分析应用的二进制代码和运行时行为。一旦苹果的加密实现存在未公开的密钥使用,比如在本地程序中引用了某个神秘常量或调用了隐藏的密钥解密函数,逆向工程往往能还原这些逻辑。专业团队通过调试、反编译、动态埋点等方式重现协议的握手过程,查看每一步骤所用的密钥材料。如果过程中出现与官方文档不符的环节(例如本应由用户设备生成的密钥却从外部获取),将立即引发怀疑。此外,安全社区定期举办的漏洞挖掘和破解挑战赛也扮演重要角色——顶尖黑客会竞相攻破苹果设备的加密层,并公开报告发现的问题。过去这些努力揭示了一些实现漏洞(如内存越界、0day攻击途径),但从未曝出“苹果预留万能密钥”之类的后门。一例典型事件是2017年有黑客成功解密了Secure Enclave固件以研究其中机理,结果证实即便取得固件代码,攻击者仍无法提取到任何用户密钥或后门凭证ciso.economictimes.indiatimes.com。这一结论进一步增强了业界对苹果加密实现中无后门的信心。
-
网络流量与协议行为分析:加密协议往往涉及设备与服务器的交互流程。研究人员会抓包和监控这些网络流量,分析协议握手时交换的消息格式和内容。如果苹果尝试在密钥协商时暗中插入自己的公钥或请求额外数据,流量分析将捕捉到异常的报文模式。例如,在正常的端到端加密通信中,设备之间交换彼此的公钥证书,不应有第三方公钥悄然出现。而所谓“幽灵用户”后门提案正是要求服务提供商在群聊中偷偷加入一个看不见的第三方公钥。这样的方案被广泛批评因为它破坏了用户验证通信对端身份的机制,需要服务器隐藏通知才能欺骗用户lawfaremedia.org。密码学家指出,这将削弱认证过程并带来新漏洞,因此难以在不被发现的情况下实施lawfaremedia.org。由此可见,通过流量异常识别潜在后门是切实可行的。当年的GCHQ“幽灵用户”建议一提出,就被包括苹果在内的业界联合抵制,47家机构和专家联名公开信指出该做法“对网络安全构成严重威胁”internetsociety.orgsilicon.co.uk,可见社区对这类后门手段有高度警惕性。
-
独立审计和信任链验证:许多安全敏感的加密功能会接受独立机构的审计,以建立公众信任。比如苹果的 iCloud 钥匙串(Keychain) 采用多层加密和信任链机制,其设计文档表明敏感信息的密钥始终需要Secure Enclave参与才能解锁techrepublic.com。有第三方评估指出,钥匙串中的私密数据即便保存在云端也是经过高强度加密的,任何人(包括苹果)都无法直接读取明文techrepublic.com。这一架构经过多轮外部安全会议研讨和学者研究,至今未出现被植入后门的迹象。同样,苹果设备中的 Secure Enclave 安全隔区 也多次成为学术研究和黑客大会的焦点。研究人员通过攻击Secure Enclave找出了少数漏洞(例如早期A7-A11芯片存在硬件级漏洞ciso.economictimes.indiatimes.comciso.economictimes.indiatimes.com),但这些漏洞只是实现瑕疵,并非有意留出的后门。实际上,正是这些公开的审计和破解挑战证明了Secure Enclave的设计初衷:即使攻击者获得硬件或固件访问权,仍无法提取出主密钥ciso.economictimes.indiatimes.com。学术界和白帽黑客社区通过反复的审查和渗透测试,为苹果的“零后门”承诺提供了有力的背书。换言之,加密社区的独立审计机制确保了任何后门都难以隐藏;只有经得起各方检验的系统,才能真正赢得用户信任。
综上所述,在强大的社区监督下,任何后门密钥的存在都会留下蛛丝马迹,并最终被曝光。无论是协议分析、逆向工程还是实网监测,多层次的手段使得厂商无法神不知鬼不觉地在成熟加密方案中藏入后门。这也是为什么苹果等公司反复强调没有后门:一旦撒谎,终将被揭穿,信用荡然无存。
iCloud 钥匙串信任链下的全局数据加密密钥(DEK)机制研究
苹果的高级数据保护(Advanced Data Protection)引入了端到端加密,将大部分 iCloud 数据的密钥仅存储在用户的受信设备上support.apple.com。在该机制下,每个用户的 iCloud 帐户针对各数据类别生成自己的“全局”数据加密密钥(Data Encryption Key, DEK),这些密钥受 iCloud 钥匙串的信任链机制保护。下面将详细探讨全局 DEK 的生成、分发与封装,多设备场景下的生命周期变化,以及苹果保障 DEK 安全和确保服务器从未获取明文 DEK 的技术手段。
全局 DEK 的生成、更新与轮换
初始生成:当用户首次在支持的设备上启用高级数据保护时(需运行 iOS 16.2、macOS 13.1 等新版系统,并开启双重认证),系统会在该设备上本地生成全局数据加密密钥。实际上,每个受端到端加密保护的 iCloud 服务(例如云备份、照片、笔记等)都有各自的 CloudKit 服务密钥对,其私钥用作该类别数据的主加密密钥support.apple.comsupport.apple.com。这些服务密钥使用安全随机算法在用户受信设备上创建,具有唯一性,并由设备的安全硬件保护。启用高级数据保护时,设备会将之前由苹果保存的云端密钥从苹果的硬件安全模块(HSM)中删除,并生成新的服务密钥,以改用仅存储在用户设备上的密钥来加密云端数据support.apple.comsupport.apple.com。这一过程确保全局 DEK(即各服务的新密钥)仅存在于用户受信设备上,苹果服务器端不再持有其副本。
是否变化及何时变化:在正常使用中,全局 DEK(各服务密钥)的私钥一经生成会保持稳定,用于持续加密解密用户数据,并不会频繁更换。唯有在特定事件下才会轮换或更新密钥,例如用户启用高级数据保护时系统触发的一次性密钥轮换,以及用户后来关闭高级数据保护或怀疑密钥泄露时的情况support.apple.com。苹果文档指出,当用户打开高级数据保护时,设备会启动异步密钥轮换操作,为此前存储于苹果服务器的每个服务创建新的服务密钥support.apple.com。新数据随后使用新密钥加密,旧密钥无法解密新数据support.apple.com。同样地,当用户关闭高级数据保护返回标准保护时,设备会将原本仅存于本地的新密钥上传回苹果HSM,并可恢复使用先前的旧密钥support.apple.com。因此,可以总结:初始启用高级保护时会生成并切换到新的全局 DEK,此后这些密钥保持不变;如用户关闭功能则恢复旧密钥;除非再次启用或发生安全事件,系统通常不会主动更换全局 DEK。
值得注意的是,在极端情况下如果用户怀疑密钥泄露或设备失窃,用户可以选择通过重置整个端到端加密环境(例如先关闭再重新开启高级数据保护)来触发新的 DEK 生成,从而保护云端数据安全。然而,此操作会要求所有设备重新加入信任链,并重新上传数据副本加密后存储。
多设备环境下 DEK 的分发与封装
信任链机制: 苹果使用 iCloud 钥匙串的信任链(又称同步圈,circle of trust)来在多设备间安全同步全局 DEK。启用了高级数据保护后,属于用户 Apple ID 的所有受信设备共同构成一个加密信任链,每台设备都有一对用于同步的非对称椭圆曲线密钥(如 P-384)support.apple.com。当第一台设备生成全局 DEK 后,它会将这些密钥加入自身的 iCloud 钥匙串保护域,并通过 CloudKit 安全地共享给用户的其他设备support.apple.com。具体而言,设备会维护一份受信设备的公钥列表,并使用自身的私钥对列表签名后存储于 iCloud;只有持有用户账户密码或设备私钥者才能读取或篡改这份列表support.apple.com。这一机制保证了只有经过用户授权加入信任链的设备才能获取 DEK,其余任何第三方(包括苹果服务器)都无法读取信任链中的密钥数据support.apple.com。
密钥传递与封装:在多设备场景下,每台设备都会持有全局 DEK(各服务私钥)的一个副本,但这些副本始终以安全加密形式封装后再传输和存储。例如,当用户新增一台受信设备时,新设备会生成自己的同步密钥对并向云端发出加入信任链的请求support.apple.com。已有的一台受信设备(通常是用户主动在其上同意新增设备)会验证该请求并通过 设备间安全信道 传输 DEK 副本给新设备support.apple.com。在此过程中,现有设备会利用新设备的公钥来加密封装 DEK,或双方通过椭圆曲线 Diffie-Hellman(ECDH)协商会话密钥来传递 DEK,从而确保只有目标新设备能解开密钥包装。苹果未公开具体用哪种算法封装,但业界常用方案包括 AES 密钥封装算法(AES-KW) 或 AES-GCM 算法 对会话密钥加密support.apple.comsupport.apple.com。可以推测,Apple 采用了符合 NIST 标准的 AES-256 算法对对称 DEK 进行二次加密包装,并结合设备的非对称密钥进行密钥交换/加密,以实现端到端的安全传递。
本地存储与保护:当设备接收到封装的 DEK 后,会在本地将其解密并安全保存于设备的 Keychain 中。所有 DEK 私钥仅存在于设备的安全隔区中,例如 iPhone 的密钥保存在 Data Protection 类钥匙串项下,并受 Secure Enclave 协处理器保护(访问需通过用户设备解锁)support.apple.com。这样设计保证即使设备遗失或被攻破,未解锁状态下设备上的 DEK 依然难以提取。总之,多设备环境下,每台受信设备都持有全局 DEK 副本,但始终通过端到端加密的方式同步与存储:传输过程中使用公钥加密/会话密钥,存储时依赖设备硬件密钥封装技术(如 Secure Enclave 提供的UID派生密钥)进一步加密,最大程度降低密钥泄露风险。
设备新增、移除与丢失场景下 DEK 和数据的生命周期
新设备加入: 当用户在新设备上登入 iCloud 并启用高级数据保护时,该设备无法直接访问云端受保护数据,需要首先加入信任链。加入流程包括:新设备生成自己的同步密钥对并将公钥提交给苹果云端(CloudKit)support.apple.com;苹果服务器将此请求传达给用户已有的一台受信设备上,提醒用户有新设备申请加入。用户在已有设备上批准请求(需输入密码或通过生物识别验证身份),之后已有设备会将新设备的公钥添加到信任链并再次用自己的私钥和账户密码派生密钥签署信任圈数据support.apple.com。随后,该已有设备通过上述安全信道,将全局 DEK 的加密副本传送给新设备support.apple.com。一旦新设备成功解密获得 DEK,它就加入了受信设备列表,可以像其他设备一样解密云端的端到端加密数据。整个过程确保只有获得用户明示批准的新设备才能获取 DEK support.apple.com。
设备移除与更换:当用户从 Apple ID 中移除某台设备,或设备被抹除/重置时,该设备将不再被视为信任链的一员。此时其他仍在线的受信设备会更新信任链状态,将该设备的身份从受信列表中剔除support.apple.com。需要强调的是,移除设备本身并不会导致全局 DEK 自动更改。被移除的设备虽曾持有 DEK 副本,但一旦不再受信,其无法从苹果服务器获取新的数据更新,而且由于设备已从账户移除或被抹掉,攻击者无法再借此解密云端后续的数据。苹果并未设定在每次设备变动时轮换密钥,这是出于实用性的考虑——频繁更换 DEK 将要求对云端大量数据重新加密,代价高昂。不过,若某台设备遗失且用户怀疑其本地密钥可能泄露,用户可以选择手动采取措施,例如从 iCloud 设置中移除此设备并重置高级数据保护(关闭再开启),从而生成新的 DEK,保护未来的数据安全。
云端数据影响: 当设备移除或失效时,云端已经加密的数据依旧由原来的 DEK 保护,并不会因为设备离开而重新加密。只要用户其他任一受信设备仍保存着该 DEK,便可继续访问此前的数据。被移除的设备由于缺失信任凭证,也无法再从服务器同步到后续新增或修改的任何机密数据(即使攻击者拥有其物理设备,由于密钥受 Secure Enclave 和设备密码保护,也难以提取support.apple.com)。因此,在多设备环境中,云端数据的可访问性取决于至少有一台受信设备存有对应 DEK。只要用户至少有一台设备或有效的恢复方式,数据就可解密使用;反之则数据陷于加密状态无法读取。
失去所有设备:高级数据保护要求用户在失去所有受信设备的极端情况下,借助预先设置的恢复机制取回 DEK。苹果强制要求启用该功能的用户提供至少一种账户恢复方法(例如指定恢复联系人或设置恢复密钥)support.apple.comsupport.apple.com。当用户所有设备均遗失或不可用时,只有通过这些恢复方式才能重获对数据的访问权。具体而言,如果用户提前设置了恢复密钥(一串随机生成的28位字符)并安全保存,那么此时用户可在新设备上登陆 Apple ID,并输入该恢复密钥来恢复数据。苹果服务器会将一份加密的 DEK 备份( escrow 记录 )下发到新设备,而新设备利用用户提供的恢复密钥将其解密,提取出全局 DEKsupport.apple.comsupport.apple.com。由于恢复密钥是由用户掌控、苹果不存储明文的要素,只有提供正确密钥的新设备才能解开 escrow 获得 DEK。在成功恢复后,新设备将重建信任链,并可以访问之前端到端加密的所有云端数据。
若用户选择的是恢复联系人,流程类似:用户联系预先设定的可信联系人,由联系人通过其苹果设备生成一个验证代码提供给用户。用户在新设备上输入该代码后,苹果同样将加密的 DEK 备份下发,新设备据此恢复密钥。整个恢复流程依然遵循端到端加密原则:苹果仅充当中转并验证权限,但并不知晓用户的实际 DEK 内容support.apple.com。
不可恢复的情况:如果用户既没有其他受信设备、又未设置任何恢复联系人或恢复密钥,那么全局 DEK 将无法找回,相应的云端数据也就永久处于加密不可读状态support.apple.com。苹果明确表示,若用户丢失所有设备且无恢复方式,公司无法帮助用户恢复这部分端到端加密的数据support.apple.com。这凸显了高级数据保护的一个权衡:安全性增强的同时,数据恢复的责任完全由用户自担。因此用户需谨慎管理受信设备和恢复选项,以避免陷入无法解密个人数据的境地。
DEK 安全性的密码学保障机制
苹果在高级数据保护与 iCloud 钥匙串架构中运用了多种密码学机制来保障 DEK 的机密性和完整性,包括密钥封装、密钥派生、硬件安全模块,以及严格的权限控制:
-
端到端加密与密钥层级化:如上所述,iCloud 采用分层密钥架构对数据加密。以 CloudKit 私有数据库为例,每位用户有一个顶层的 CloudKit 服务密钥对,其私钥用来保护下层对称密钥(如 Zone密钥、Record记录密钥等)
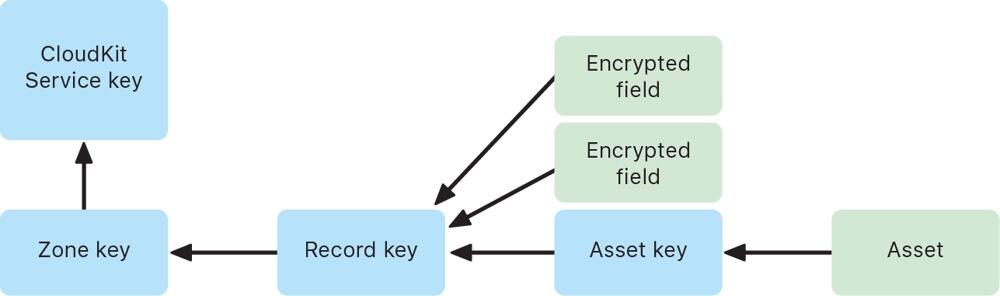 support.apple.com。当用户在设备上写入数据时,会生成记录级别的随机对称密钥加密数据字段,再逐层用上级密钥封装这些对称密钥。具体来说,记录密钥用 Zone 密钥加密,Zone 密钥再用全局服务公钥加密(即 DEK 公钥),形成多层密钥封装结构support.apple.com。只有持有最顶层私钥(DEK 私钥)的受信设备才能逐层解开封装,最终解密出用户数据。通过这种分层加密与密钥隔离设计,即使某一层的密钥泄露,攻击者也无法直接获取上层密钥或明文数据。
support.apple.com。当用户在设备上写入数据时,会生成记录级别的随机对称密钥加密数据字段,再逐层用上级密钥封装这些对称密钥。具体来说,记录密钥用 Zone 密钥加密,Zone 密钥再用全局服务公钥加密(即 DEK 公钥),形成多层密钥封装结构support.apple.com。只有持有最顶层私钥(DEK 私钥)的受信设备才能逐层解开封装,最终解密出用户数据。通过这种分层加密与密钥隔离设计,即使某一层的密钥泄露,攻击者也无法直接获取上层密钥或明文数据。 -
AES 密钥封装与封闭式硬件存储:苹果广泛采用了经验证的对称加密算法来封装和存储 DEK。传输过程中的 DEK(或下层对称密钥)通常通过 AES-256 算法加密封装后再上传support.apple.com。一种常用方法是 AES 密钥包装 (AES-KW),它专门用于用一个对称密钥安全地封装另一个密钥,确保密钥材料在传输中不暴露。与此同时,设备本地的 DEK 私钥会存储在受 Secure Enclave 保护的区域。Secure Enclave 为每台设备提供唯一的硬件 UID 密钥,仅用于解锁设备密钥袋和钥匙串项support.apple.com。也就是说, DEK 私钥本身可能被进一步用设备硬件密钥加密(这相当于在软件密钥之外又加了一道硬件锁)。只有当用户解锁设备并通过身份验证,操作系统才能调用 Secure Enclave 解封这些密钥用于加解密操作。通过AES-GCM 等对称加密结合Secure Enclave 硬件密钥封装,苹果确保 DEK 无论在云端传输还是本地存储,都始终处于加密状态,降低被截获或提取的风险support.apple.com。
-
椭圆曲线密码与密钥交换: 信任链中设备互认和密钥共享依赖椭圆曲线密码算法。每台设备的同步身份密钥对采用强大的 P-256 或 P-384 曲线support.apple.comsupport.apple.com。当新设备加入时,已有设备会利用椭圆曲线数字签名算法 (ECDSA) 对信任链数据签名校验,防止伪造support.apple.com。同时,在设备间传输 DEK 时,可能使用椭圆曲线 Diffie-Hellman (ECDH) 来建立共享密钥,加密传输内容。ECDH 可确保即使通信被窃听,攻击者无法推导出会话密钥,因而无法获取密钥内容。综上,非对称加密和密钥交换协议保证了只有合法设备才能参与密钥同步,新设备的引入需要现有设备用其私钥签名确认,杜绝中间人攻击或伪造信任链的可能。
-
密钥派生函数 (KDF):在某些步骤中,苹果使用了密钥派生函数强化密码。历史上,iCloud 钥匙串曾要求用户设置 iCloud 安全码时,将用户密码通过 PBKDF2 等KDF算法派生出密钥,用于签名和加密信任圈hackmag.comhackmag.com。即便在新的双重认证架构下,某些场景仍可能涉及KDF——例如恢复密钥或联系人代码很可能通过 KDF 转换为实际用于解密 escrow 密文的密钥材料。这些 KDF 算法引入高强度的盐值和大量迭代运算hackmag.com,增强了抗暴力破解能力,防止弱口令被攻击者猜测。总之,KDF 的应用确保从用户口令/恢复码到加密密钥的映射具有单向性和计算复杂度,进一步保护 DEK 相关流程的安全。
服务器无权获取明文 DEK 的保障
苹果的设计宗旨是在云端架起“盲墙”,确保服务器既无权也无实能接触用户 DEK 的明文,这也是实现“即使云端泄露,用户数据仍安全”的关键:
-
密钥仅存在于用户端: 开启高级数据保护后,所有主要 iCloud 数据类别的加密密钥仅存储于用户受信设备(或用户掌握的恢复载体)中,苹果服务器端不再保存这些密钥support.apple.com。文档明确指出,启用该功能后,苹果“无法读取或访问用户的服务密钥”support.apple.com。即在正常运行过程中,苹果的云服务器从未拥有解锁用户端到端加密数据所需的密钥。服务器所见到的只是由用户设备加密后的数据碎片,对其而言是不可解密的黑箱。
-
云端存储密文及加密元数据:iCloud 服务器虽然需要存储用户数据(如云照片、备忘录的加密内容),但这些内容均已由设备使用 DEK 加密完成。即便是为了提供某些功能,云端保留了少量未加密的元数据(如文件校验和用于重复数据消除),这些元数据也不包含可用于推导 DEK 的信息support.apple.comsupport.apple.com。苹果正在致力于将更多此类元数据也纳入端到端加密范围,以进一步减少明文暴露面support.apple.com。此外,CloudKit 框架要求开发者在模式中明确标记需要加密的字段,未标记的字段(例如排序用的时间戳)即便明文存储,亦不涉及敏感内容support.apple.com。由此,云服务器始终缺乏关于 DEK 或用户敏感数据的明文,一旦发生数据泄露或内部越权,攻击者拿到的也只是高强度加密下的乱码。
-
权限架构防范后门访问:苹果构建的信任链机制也防止了服务器假借授权来获取密钥的可能性。服务器不能私自添加受信设备或篡改信任链,因为每次信任链更新都需要现有设备的私钥签名以及(在老架构下)用户密码派生密钥的二次签名hackmag.comsupport.apple.com。苹果服务器既不持有用户设备私钥,也不知晓用户密码,因此无法伪造这些签名来诱导其他设备信任一个恶意设备。即使在双重认证体系下,服务器在设备加入流程中充当中继,并没有能力绕过用户批准直接将新设备植入圈内support.apple.comsupport.apple.com。这种架构等于为服务器访问用户密钥设置了密码学上的禁区。正如苹果安全白皮书所言,在最坏情形下如果用户丢失对 iCloud 钥匙串和其恢复机制的访问,那么相应的端到端加密数据苹果也无力恢复support.apple.com。苹果通过制度和技术结合,确保即便政府或机构要求提供用户数据,由于公司本身并无解密能力,只能交出加密的内容。
综上所述,Apple 高级数据保护下,全局数据加密密钥的生成由用户设备掌控,借助 iCloud 钥匙串信任链在多设备间安全同步。无论是在设备增加、移除还是用户失去设备的情况下,密钥和数据的生命周期管理均以用户掌控为中心:只要用户保有至少一个密钥载体(设备或恢复方式),数据即可解密使用;反之苹果也无法绕过用户获取密钥明文support.apple.com。苹果通过成熟的加密算法(AES-KW、ECDH 等)、硬件支持(Secure Enclave)、密钥分层与派生策略,实现了“零信任”云存储:服务器对用户密钥一无所知,从而使用户云端数据获得前所未有的保密性提升。
附录
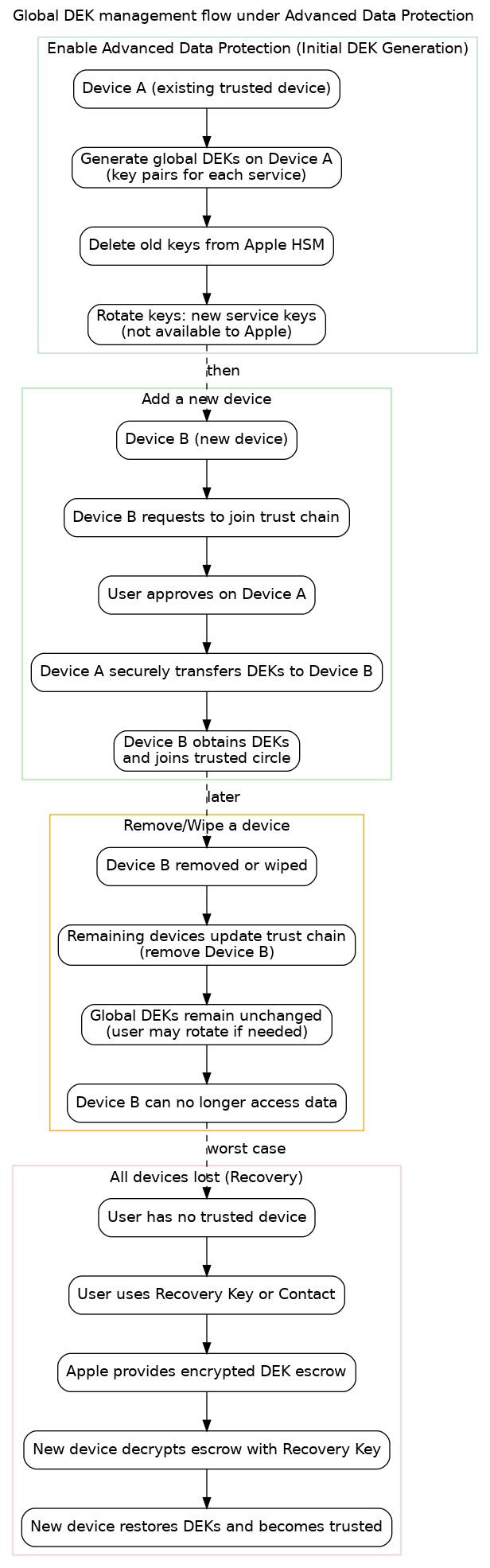 图:高级数据保护下全局 DEK 管理的流程示意图。包含初始启用(设备 A 上生成新密钥并删除苹果服务器密钥)、新设备加入信任链(设备 B 请求并由设备 A 批准传输密钥)、设备移除或丢失(更新信任列表,但密钥通常不变)、以及用户失去所有设备时的恢复流程(通过恢复密钥取回 DEK)。各阶段均保证 DEK 安全不被未授权实体获取。
图:高级数据保护下全局 DEK 管理的流程示意图。包含初始启用(设备 A 上生成新密钥并删除苹果服务器密钥)、新设备加入信任链(设备 B 请求并由设备 A 批准传输密钥)、设备移除或丢失(更新信任列表,但密钥通常不变)、以及用户失去所有设备时的恢复流程(通过恢复密钥取回 DEK)。各阶段均保证 DEK 安全不被未授权实体获取。 -
-
 @ bc6ccd13:f53098e4
2025-05-24 15:55:20
@ bc6ccd13:f53098e4
2025-05-24 15:55:20It wasn’t so long ago that the mainstream conversation around population was exclusively focused on the dangers of overpopulation. The fatal flaws in the Malthusian theory had yet to be disproven clearly and obviously by observable demographic trends. That’s been gradually changing, and while it’s hardly a mainstream consensus, concerns about falling birthrates and the risk of population collapse have taken over the population conversion on the political right, and sometimes beyond.
There’s no questioning the data at this point. Fertility rates over most of the world have been in precipitous decline, and if the current trajectory continues, global population will peak very soon and fall rather dramatically. And even the falling population itself is much less of a threat than the aging population that will inevitably precede it. Having a large cohort of older and retired people and a small cohort of young workers is an existential threat to the modern welfare state, and to the entire credit-based fiat monetary system that supports it. But that’s a subject for another day.
There are a multitude of different theories that attempt to explain why this is happening. I’ll name some of the most common ones:
-
Increased education and employment opportunities for women
-
Urbanization
-
Economic factors
-
Access to contraception
-
Changing social and cultural norms
-
Delayed marriage
-
Improvements in infant mortality rates
-
Government policies
-
Environmental concerns
-
Pornography
-
Feminism
-
Endocrine disrupting chemicals
-
Dating apps
Most rational thinkers agree there must be multiple factors playing a role. But the fact that the problem is so wide-spread, and populations that seem to be resisting the trend are so rare, shows that the strongest underlying factors are cross-culturally powerful and not easily resisted or reversed with marginal cultural differences and standard public policy efforts.
While populations that resist the trend are rare, they are not quite non-existent. A few groups stand out for their persistently high fertility rates. On a geographic basis, sub-Saharan Africa is the only major region still maintaining above-replacement fertility rates. For various reasons, I don’t think Africa is the most useful place to look for answers on what’s causing the decline elsewhere or how it could be reversed. One reason is that Africa seems to be following the global pattern, just with a lag. In another few decades the data may look very different, just like it does for South America today compared to 20 years ago.
In my opinion, a more useful place to look for data is in smaller population sub-groups within a geographic area that have fertility rates significantly higher than the general population levels. Rural populations in general have higher fertility rates than urban populations, but the difference isn’t really enough to consider it significant. The groups that fit this category well seem to be exclusively religious. These include certain Christian denominations in the traditional Anabaptist category including the Amish, Mennonites, and Hutterites, Muslims in some areas, and Jews, particularly the most orthodox sects. Mormons recently fell out of the high-fertility religious group category, which would also make for some interesting research.
It would be fascinating to compare these groups and see what they have in common outside just being religious in nature. I don’t have the knowledge to make that comparison. Instead, I’m going to focus on the group that’s often referenced and analyzed by people without much personal knowledge, the Amish.
I have read numerous articles and comments that reference the Amish to support this or that theory on the cause of falling fertility. One thing I notice is an obvious lack of understanding of the Amish culture, which leads to faulty arguments that don’t reflect reality. This isn’t surprising, given the insular and poorly-understood nature of the culture, the plethora of ridiculously incorrect “Amish” reality TV shows and pop culture myths, and the fact that the number of people with firsthand knowledge of Amish culture from an insider perspective who also write about demographic trends on any public platform is probably zero.
Well, was zero. I’m about to make that one.
My Qualifications
Since I’m claiming to have this knowledge, it’s only fair to give a little background as to how I got it. I choose to stay anonymous on the internet, and given that this is personal information that could make it significantly easier to dox me, I’ll be deliberately vague.
My parents were both born in Amish families. They didn’t stay, opting to leave the Amish church and culture before getting married and starting their family. My grandparents were all Amish, and all my cousins and most of my extended family remain Amish to this day. My parents didn’t move out of the Amish community, staying in the area and joining a conservative Mennonite church that was about the closest thing to being Amish without actually being Amish. The Mennonite community has a generally good relationship with and a lot of respect for the Amish community, given their deep similarities and shared history and cultural background.
I grew up interacting regularly with Amish relatives, neighbors and community members, speaking the Pennsylvania Dutch my parents taught us and used exclusively at home. I’m very certain that a real deep understanding of Amish culture is almost impossible without speaking their language, just like many other cultures around the world. The Amish speak English as their second language, but there are aspects of their culture that aren’t spoken about in English.
This lifelong proximity to and interaction with the Amish community has, I believe, given me some unique insights into the factors supporting their high fertility rates that no amount of academic research will ever uncover.
Who are the Amish?
First, some basics.
The Amish are a traditionalist Christian denomination. The way to understand the Amish is as a religious denomination first, and a culture second. Getting the two mixed up makes it impossible to understand why the Amish live the way they do.
Sure, their unique lifestyles makes them noteworthy as a group. But that lifestyle is based on and maintained by their religious beliefs and convictions.
Fundamentally, the Amish attempt to live out the Gospel as Jesus taught in the Sermon on the Mount. They believe their church has done so historically, and that the best way to make sure they keep doing so in the future is to view any changes to their traditional lifestyle with extreme skepticism and resistance.
The two primary doctrines that separate them from the mainstream Protestant Reformation, which is their group’s origin, are the doctrines of nonconformity and nonresistance. They apply the doctrine of nonconformity, the command to “be not conformed to this world: but be ye transformed by the renewing of your mind, that ye may prove what is that good, and acceptable, and perfect, will of God” in both a spiritual and a practical sense. They believe that Christians are to be radically different from non-Christians, both in their beliefs and attitudes, and in their lifestyle and appearance. And they apply the command to “resist not evil”, nonresistance, to mean that it’s a sin to use physical force or violence against another person for any reason whatsoever. They don’t make any exception for military service of any type, which they object to as a matter of conscience, or for self-defense, which they refuse to engage in even if it means death for themselves or their family.
The Amish do not practice infant baptism. Their young people must choose to be baptized and formally become members of the church, usually in their late teens or early twenties. As part of the baptism ceremony, they make a vow to remain faithful to God and the church until death. The Amish, as a church, interpret this vow to mean that the new church member will remain a member of the Amish church for life. Leaving the Amish church after making this vow and being baptized is viewed as breaking the vow, and is the justification for their practice of shunning, or the ban. Those who do so are cut off from contact with the community in various ways. Typically they won’t eat a meal with a shunned person, ride in a car a shunned person is driving, or do business with a shunned person. That includes immediate family. Failure to enforce this shunning against someone, even your own child, can result in running afoul of the church leadership and also being excommunicated and shunned.
This punishment, however, only applies to people who leave the church after baptism. Those young people who choose not to be baptized and leave the church instead are free to be treated just like any other non-Amish person, although their family essentially disown them and treat them like a shunned person anyway, if they’re especially strict and upset about the betrayal of Amish values.
Most Amish people don’t believe that the Amish are the only true church, or that only Amish people are true Christians. Most are accepting of other conservative Anabaptist denominations, and respect their values and practices as a different but valid way to be Christian. Church teaching strongly suggests that those who fall under the ban are living in sin and won’t make it to heaven. Most individuals, though, probably wouldn’t agree with that in every case if they were free to give their true opinion on the issue.
The Amish maintain a fertility rate of around 6 to 7 children per woman. Some recent research suggests this may be starting to fall somewhat, but the data isn’t extensive enough to make a solid judgement yet.
There are a wide variety of different “flavors” of Amish in different areas of the US, a fact they’re very aware of. The data strongly indicates that the most conservative and technologically primitive communities have slightly higher fertility rates and significantly higher retention rates of young people.
Why do the Amish Maintain High Fertility Rates?
Okay, enough background. Time to dive into the reasons I believe the Amish maintain their historically high fertility rate despite living in a developed, modern economy surrounded by people with dramatically sub-replacement fertility rates.
I thought long and hard about the best way to approach this. Going through a list of factors topically seemed like the obvious one. But the more I thought it through, the less I liked it. For one, how do you arrange the factors? Order of importance? How do you decide that? Also, the factors are so inter-related that they’ll be very tough to separate and understand individually. Finally, it seems dry and boring. Nobody needs that.
So I’m going to try something different. I’m going to approach it from a narrative angle. I’ll try to describe the life of a typical Amish person, from birth to death, in a chronological way. That’s the best approach to present it in a way that makes the culture relatable, while also tying the different factors together logically.
I’ll describe the experience for both men and women as best I can, and try to present the various factors encouraging high fertility as I see them at the appropriate part of the story.
This will likely be an article that gets revised later to address any questions that come up, so don’t consider it the final word on the subject.
Alright, time to get started.
Subscribed
First off, this might seem obvious, but the typical Amish baby is born into a large family. On average, they’ll have 5 or 6 siblings, and more is not at all uncommon. Families of 10 won’t raise an eyebrow, and 12-16 children aren’t unheard of, especially in the past when mortality was higher and second marriages were more common among younger widowers who went on to have children with their second wife. Humans are social creatures, and the environment and people we grow up surrounded by have a strong influence on our frame of reference. Studies have shown that women are very unlikely to have more children than their mother had. The number of siblings in your family, and in families you observe and interact with, doesn’t determine the number of children you will have, but it does strongly influence the number of children you feel is a “normal” amount. That makes it a kind of ratchet effect, where it’s very unlikely that a generation raised in homes with one or two children will go on to have larger families of their own collectively.
This cultural norm of large families establishes a kind of inertia that normalizes high fertility right from birth. Amish children grow up surrounded by siblings, observing, and as they get older, helping with the care and maintenance of a large family. All their relatives, cousins and extended family are also likely to belong to large families. The average Amish child grows up with dozens of first cousins, and sometimes hundreds of more distant cousins, many of whom they likely know well and socialize with regularly. This experience establishes a mental framework where a large family is assumed to be the default. And there is no stronger human tendency than the urge to fit in with the people around you.
Amish children grow up with strong gender norms taught from a very young age. The Amish culture follows strict and conservative gender roles. Boys and men do male things, girls and women do female things, and there is little effort or desire to create any overlapping space.
Boys grow up doing traditionally masculine things. They play outside, do chores on the farm, help their dad with his work, probably get a BB gun before age 10, go hunting and fishing, play sports, and generally prepare for a lifetime of physical labor and providing for a wife and family.
Girls grow up doing traditionally feminine things. They help care for younger siblings, help with housework, play with dolls, learn to cook and preserve food, learn to sew, and generally prepare for a lifetime of caring for and raising children and maintaining a large household.
It’s a common misconception that the Amish are mostly farmers who live off the land, subsistence style. That’s not at all accurate. While there are still Amish who make their living farming, at least in some areas, that has become the exception. The large scale of modern agriculture means it takes a lot of acres and a lot of machinery to run a profitable commercial farming operation. The Amish reject the use of most modern agricultural machinery, which makes them uncompetitive in commercial agriculture outside more niche markets like dairy, produce, or greenhouses. And the fact that they live in small geographic communities with large families means they quickly buy up all available farmland in an area until they price themselves out of the market. Prime farmland in heavy Amish farming communities like Lancaster, Pennsylvania routinely sells for over $25,000 per acre, which is more than a commercial crop farming operation might bring in over a lifetime.
So the Amish have moved away from a primarily agriculture based economy to various other occupations. In some areas they work in RV factories. Most work in trades, primarily construction. Many are masons, carpenters, cabinet builders, mechanics, welders, etc.
But they reject the ownership of cars, so they still use their characteristic horses and buggies for transportation. In reality, they use cars for most of their transportation needs. But they don’t own cars or have driver’s licenses, so they rely on “Amish taxi drivers” to chauffer them around. The men hire a driver to take them to and from work, if they work in construction or some other job outside the home. The women hire a driver take them to town for their shopping or for other errands. The exception is church. They’re still required to drive to church in a horse and buggy, so every family must keep a horse for that reason, as a bare minimum. In many cases that’s the only time they ever use a horse and buggy, and if it weren’t for that requirement they wouldn’t own one at all.
But that requirement means every Amish family must own enough land to keep a horse, which takes a few acres and a small barn at minimum. This forces them to live in rural areas and raise their families in a somewhat agricultural environment, even if their occupation wouldn’t require that at all. So there are always chores for the children, animals to care for, and space to play outside with their siblings.
Amish children grow up with very limited exposure to mainstream cultural pressures. Their mothers inevitably raise them at home until they start school. They don’t have TV or cell phones, so they aren’t exposed to any mainstream culture on a daily basis.
The Amish have their own schools, typically small one room schools within walking distance of all the families who attend. The teachers are often young single people, always Amish. They primarily teach basic academics: reading, writing, arithmetic, geography, history, etc. While the Amish speak both English and Pennsylvania Dutch, many Amish children are first exposed to English on a daily basis when they start school. School is taught in English, although there is limited teaching of the High German the Amish use in their church services.
Amish children attend school until 8th grade. The schools run the minimum number of days required by the state, usually 160. There is no higher education beyond grade 8. No Amish attend college.
Amish children are taught from little up that they are not like other people. The differences between their culture and mainstream culture are emphasized, and Amish culture is praised as the ideal, at a religious level. They're taught that the way to do what’s right is to do what the church asks, and those who don’t do what the church asks are in the wrong.
The Amish rate and describe everyone on a scale from “high” to “low”. A person who isn’t Amish, who isn’t a Christian, is a “high” person, or an “English” person. To go from being Amish to being “English” is the worst, most damning, failure imaginable. The Amish are “low” people. The more strict and traditional an Amish sect, the “lower” they are. Being “low” is seen as a virtue. Other conservative Christian denominations, particularly other Anabaptist groups, are also considered “low” people and generally viewed favorably, but they aren’t as “low” as the Amish.
Amish boys grow up expecting to start work full time at age 14, and to work at some type of trade or physical labor. There are no white-collar career tracks, essentially. Entrepreneurship is encouraged, and many young Amish men start their own construction crew or home business in their 20s or 30s after a few years of experience working for someone else. Often Amish boys start off working for and with their dad, in whatever trade or business he operates. But if they’re not interested in that particular occupation, they’re free to find another. Amish businesses and tradesmen are always willing to hire young Amish boys and train them in a craft. A good work ethic is considered a virtue, and Amish are known for their skilled craftsmanship and willingness to work harder than the competition. These traits are taught and encouraged from little on up.
Amish men as a whole do very well financially. For one, they start working and developing skills and work ethic a decade earlier than the typical college graduate. The trades pay well, and of course anyone could take advantage of that, but the mainstream narrative discourages men from pursuing a trade career by labeling it low status and keeping them in education until their prime years to gain a work ethic are past. It’s not uncommon for young Amish men just out of 8th grade to land a job on a carpentry crew for $25-30 an hour. With bonuses, some of them are bringing in $90k/year before age 20. Another advantage young Amish men have is lower expenses. They can certainly find places to spend their money, typically hobbies like hunting and fishing, but things like expensive designer clothes and accessories or overpriced car payments aren’t really an option. They also benefit from the Amish exemption to Social Security taxes. The Amish don’t pay into or collect Social Security. More on that later, but it helps immensely to keep more of your paycheck in your early prime working years.
Amish girls grow up expecting to get married at a young age and raise a large family as a traditional housewife. Amish girls aren’t encouraged to have a “career”, and the idea would be silly to them. They are expected to work, but the work is either helping their mom with the household, working on the family farm or business, or doing something like teaching school or working at an Amish farmer’s market to pass the time between leaving school and marriage. It’s never viewed as a permanent occupation, because marriage and motherhood is the default aspirational lifestyle. A common job for young Amish girls is working as a “maid” to help a new mother with housework at the end of pregnancy and for the first few months after childbirth. All new mothers can get this type of help if they want, and it will usually be a younger sister, cousin, or niece of appropriate age. Otherwise the community will find a suitable girl who’s available for the job. A “maid” will sometimes travel to a different Amish community for this reason, given how large extended families are and how frequently Amish families move across the country to a different community. This is often an opportunity for them to attract the attention of a young man outside their local community, and is one of the only ways for a long-distance relationship and marriage to begin.
Amish young people are expected to live with their parents until marriage, with very few exceptions. They’re also typically expected to work for their dad in the family business for no pay, and to give any earnings they make at a day job outside the home to their parents. This is typically expected until age 21, or until they get married, whichever comes first. More recently, with the rising cost of land and housing, it’s becoming more common to make age 18 the cutoff. And when a young couple is engaged, the parents typically allow them to start saving their income for their future household. This practice helps parents offset some of the expenses of raising such large families, along with the fact that no money is spent on higher education. It also provides one strong incentive to marry as early as possible.
Amish culture revolves around family and the community. Extended families are large, and people are expected to know and interact with their family. Conversation with a stranger at a social event invariably starts by asking their name, then asking who their parents, grandparents, and other relatives are until some distant family connection or a mutual acquaintance is found. Since the Amish community has a small pool of family names, and tends to heavily favor certain Biblical first names, enough people end up with the same name to make things really confusing. People are often identified by two or three generations of their family, for example “Sam Yoder’s John’s Amos” for an Amos Yoder who’s father was John Yoder and grandfather Sam Yoder.
Social activities are either family events or church events, or both. Weddings and funerals are the main social functions other than church services, and people are expected to attend as many as possible among their family and extended family, regardless of the distance. Given the large family sizes, most Amish have dozens of first cousins and many more distant cousins. Weddings and funerals can be almost weekly events. These are church events as well, so much of the local Amish community will usually attend. It will be an all day event, with the women and girls preparing a lunch and dinner for everyone. After the meal, the women and girls will wash the dishes and clean up, while the men sit around and talk. No cell phones, remember. Talking is the main form of social interaction. Topics typically include work, family news, hunting and fishing stories (Amish men hunt and fish with the same enthusiasm typical American men watch sports), horses, and interesting or funny stories about family and friends. Those with a knack for entertaining oratory are well respected and appreciated in the Amish community.
Of course the women do their fair share of talking as well, in the kitchen while cleaning up after the meal, and later in the living room where they join the men after the domestic work is done. The main topics of conversation always revolve around family, immediate and extended. News travels through the Amish community faster than any social media platform, because nothing builds Amish female status more than being the first to call with the news that great uncle so-and-so was injured in a farming accident or nephew so-and-so has a new baby, along with all the pertinent details about the name, size, and health of the baby and how the mother is doing and how many grandchildren that makes in total for the lucky grandparents.
While the adults are talking, the children are free to play either inside or preferably outside. Trampolines, climbing trees, playing in the hayloft, tag, volleyball, and softball are favorite activities at various ages. The younger boys and girls typically play together, but as they get older the girls spend more time visiting while the boys prefer more structured sports. Softball is a game for boys, but volleyball is popular with mixed teams of boys and girls at any age.
Visiting relatives or other community families is also a popular social activity, especially on “in-between Sunday”. The Amish have church every other week, and the week without church is often an opportunity to visit another family. Invitations are not expected or required, and anyone stopping by will be expected to stay for dinner and into the evening. At these type of events, the older children are often expected to sit and visit with the adults. Sitting still and being quiet are mandatory skills, since church services are 2 hours or longer and held in barns or sheds without air conditioning filled with backless wooden benches. Self-discipline is not an optional virtue, because the alternative is physical discipline.
As Amish young people enter their mid teen years, they go from childhood to youth. At a certain age, usually around 15 or 16, they officially become youth and enter the stage everyone is familiar with, “rumspringa”. That’s a Pennsylvania Dutch word that translates to “running around”. The Amish use it more as a verb, but pop culture has adopted it as a noun based on some wildly inaccurate reality TV shows and depictions.
The reality is, rumspringa varies widely from community to community, mostly based on what the parents and church leaders tolerate. Remember that Amish church membership is a fully voluntary decision, and Amish young people are free to join or not, as they decide. Late teens is the typical age for that decision. In the meantime, they are free to make their own decisions, subject to their parents’ rules. Breaking the rules can mean that at some point, they won’t be welcome to live in their parents’ household any more. That’s a fairly strong deterrent to the most extreme infractions.
At this stage, young Amish men will be buying their own horse and buggy, and both boys and girls will be permitted to attend the Sunday night “singing”. This is a social activity held at someone's house on Sunday evening, involving all the youth in the community coming together for dinner, playing volleyball, and singing German hymns together. The purpose is to provide a somewhat controlled social environment for young men and women to interact and hopefully meet their future spouse. Dating couples can attend together, and dates are permitted after the formal activities, with the young men often driving their date home late at night before finally heading home themselves.
Depending on the tolerance of the community, the informal activities can be a bit more permissive than singing hymns and playing volleyball. Often the buggies will become a typical teenage party scene, with alcohol, smoking, a radio, illicit smartphones and DVD players, and some less-than-reserved interaction between boys and girls. The punishment for getting caught can be severe, but in many cases the adults tend to turn a blind eye to what’s happening, and let the young people do as they please.
A lot more could be said about the dynamics of this cultural practice, but specifics vary so much between communities that I don’t think there’s much value in doing so. The point I think is relevant to this discussion is the question of sex.
There’s no reason to go off into the weeds on how much, if any, sex occurs. Premarital sex is absolutely forbidden. Does it happen anyway? Humans being human, certainly. How much? Probably very little in most cases. Getting pregnant, or getting someone pregnant, is the one transgression with inevitable life-changing consequences. The “shotgun wedding” is alive and well among the Amish, and getting a girl pregnant means marrying her or being expelled from the Amish community permanently, no exceptions. Besides that, getting pregnant outside of marriage is the most disgraceful and shameful thing a girl could do. It happens very very rarely, put it that way.
So casual sex within the community is basically off the table. What about casual sex with “English” people? This is where the Amish cultural practices play a big role. The Amish dress very distinctly. They can’t go anywhere in their traditional clothes without being instantly recognized. They also don’t drive cars, so going somewhere means getting a ride with someone. And their parents will usually keep an eye on their plans and whereabouts. So let’s imagine how an Amish teenager might go about finding a casual sexual encounter.
First off, getting ahold of a cell phone would be essential. They need some way to communicate with the outside world, and coordinate with their “partner in crime.” A lot of Amish teenagers do this, often with the help of slightly older people who have left the Amish, but keep ties with the community, maybe an older sibling or cousin. These are often the same people who buy alcohol for Amish teens.
Then, they need to get some non-Amish clothes. Remember, every trip away from home will take a willing driver, a plausible excuse in a community where everyone knows everyone, and the guarantee of being immediately recognized if seen in public. And the Amish parents know who the “bad kids” are, the ones who left but are willing to help their younger relatives and friends break the rules. Getting caught hanging around with them will probably mean a lot less trust and a lot less freedom in the future.
For the girls, a change of “English” clothes and a new hairstyle will let them blend in quite well. Of course, they can’t be caught leaving or coming home in those clothes, or have the clothes found at home. Lots of logistical hurdles everywhere. For the boys, they have a very distinctive haircut. A new change of clothes won’t fix that. There’s really no way for them to hide the fact that they’re Amish, even if the accent and the lack of a driver’s license don’t give them away.
Assuming they manage all that, and sneak away from home undetected, how will they find someone to hook up with? They’re very insulated from popular culture, and probably not at all comfortable in typical social situations. For the girls, there’s the added risk that an accidental pregnancy, or even just getting caught, would ruin their reputation and any chance of marriage and a family in the Amish community. So they’re unlikely to even try, unless they’re already fully intending to leave the Amish for good. That only really happens if they have a guy ready to marry them outside the Amish community, for reasons I’ll get into more later. Briefly, the Amish culture and schooling leaves women poorly prepared to support themselves outside that culture.
For the boys, there’s the typical difficulty men face in finding casual sexual partners. Multiply that by the difficulty of not having a car or driver’s license, not being experienced in mainstream social norms, plus that obvious and undisguisable Amish haircut. And all that ignores the lifelong teaching that casual sex is sinful and wrong, and those who engage in it are going against the teachings of God and the church. The entire culture is specifically designed to discourage casual sex as strongly as possible, and it does an excellent job at that.
Why does that matter? Well, humans are all very much the same, with the same desires and instincts. And sex is one of the strongest of those desires. The Amish are certainly no different.
So the Amish religious practice and culture offers a very simple choice. You can choose sex outside of marriage, which will be difficult or impossible, occasional at best, and if you get caught will mean expulsion from the community your life is rooted in, and even if you don’t get caught will mean you’re committing a mortal sin that will keep you out of heaven if you don’t repent and change. Or, you can get married and have all the sex you want, and be respected and rewarded for it.
That’s really all it takes to sell the idea of marriage to most men.
When a couple does decide to get engaged, of course with permission from the girl’s father, the wedding happens within a reasonably short time, in acknowledgement of the temptation young people face in that situation.
So let’s take a little closer look at the gender differences between the choice to stay single or to marry. It’s helpful to lay out the different life paths available, and how they play out over time.
There are very few Amish who remain single throughout their life, and almost all of them are women. So let’s look at it through a man’s perspective first. What kind of life can a single Amish man expect?
First off, a lifetime of celibacy. There’s hardly any need to go further, that’s a deal breaker for most men. If they choose to stay single for some reason, most will leave the Amish completely rather than accept those terms.
So maybe it’s more useful to look at incentives for early marriage, which is the norm. I’m a strong believer that incentives create outcomes, so I’ll be taking a hard look at incentives throughout this article.
Young people are expected to live with their parents until marriage, in most cases. Remember, no going off to college either. So from age 14 on, they’re stuck living with Mom and Dad, working full time, and not even keeping their own income. That gets old fast. Getting married, moving out, and starting a family looks better every day. Besides that, Amish women do a lot to improve the lives of their men. The Amish are well known for their delicious food. Well, that’s because the Amish women cook and bake. As a single guy, moving out of Mom’s house means not getting delicious home-cooked food every day. And they don’t have an iPhone to order DoorDash either, so it’s pizza delivery, hiring a driver to go to a restaurant, or whatever you can cook yourself. And Amish boys don’t grow up learning how to cook, that’s women’s work. Same with making clothes. Amish mothers and wives sew clothes for their families, since they’re forbidden to wear commercially available clothes in general. So a single guy is dependent on his mom for new clothes as well. Same with washing clothes. Most Amish have fairly modern clothes washing machines, although they don’t use dryers. But washing and folding clothes isn’t a job most boys grow up doing, so they’re pretty lost if they have to try it.
All in all, there aren’t a lot of upsides to staying single longer than absolutely necessary. There are plenty of benefits to marriage, though. For one, marriage is seen as a necessary step to full maturity as a man. It’s even expressed as a visible marker. Single young men typically stay clean-shaven. Once they get married, shaving is completely forbidden, and they are required to grow out a full beard. So the difference between married and single men is obvious at first glance, and is acknowledged as a marker of full maturity.
Then of course there’s the sexual access. No explanation needed.
Then there are all the benefits of an improved lifestyle a stay-at-home wife provides. That includes cooking, cleaning, washing clothes, caring for a garden, preserving food, helping with farm work or chores, and helping with his business. Many Amish wives are very involved in their husband’s career or business, whether that’s managing the bookkeeping, working in the greenhouses, or helping with daily chores on the farm. While most Amish communities use quite modern household appliances, powered with batteries, kerosene, or air pressure, the work of maintaining a household is still much more involved than for the typical American household. Especially when it comes to sewing, which very few American women do at all, but which took a large percentage of women’s time only a few generations ago. Among the Amish it still does.
I’m only focusing on the incentives for marriage right now, because that’s the first step. Of course, most married couples today don’t have 5-8 children, so there’s more to the story. But universal marriage, particularly early marriage, is an essential part of the puzzle.
Shifting focus to the women, here the picture is even more clear. Almost all lifelong single Amish people are women, and that’s not by choice. The Amish still maintain the “old maid” category that used to be part of mainstream culture. Single Amish women are almost invariably single because no man offered to marry them. Here’s why.
If single life is unappealing for Amish men, it’s positively bleak for women. Marriage and family life is the aspirational goal they’re taught from little up. And for good reason.
With their eighth-grade education, and without a driver’s license and car, their income earning potential is very limited. Most young women who aren’t busy on the farm or with the family business work as schoolteachers, housecleaners, babysitters, or cooks and servers at Amish restaurants or farmers’ markets. None of these jobs pay well. Enough to buy a few personal items, but not enough to buy a house or support even one person. And while it might be acceptable for a single Amish man to eventually buy a house and move out, at some point in his late 20s or early 30s, it’s really not acceptable at any age for an Amish old maid. Those old maids typically end up living with their parents, caring for them in old age, working the same type of jobs young girls do, and probably hoping that at some point an older widower with a family will show up and propose.
Marriage has massive lifestyle benefits for women, even more so than for men. Amish men typically do well financially, and often work in construction as well, or have friends and relatives who do. Amish houses are very nice and well constructed to say the least, and the wife gets the house she wants, the way she wants it. Being stingy with a house for your wife isn’t part of an Amish man’s mentality. Amish women are well rewarded for all their hard work keeping house, with a house they’ll be happy keeping. And of course a nice farm or at least some acreage, with space for a big garden, a barn for any animals, and space for greenhouses or whatever she needs for any home business ambitions she might have.
Along with that, Amish women have a lot of flexibility when it comes to spending money. Many Amish women handle most of the family finances. And the money her husband earns is family money, not his money. While the husband has final say in financial decisions, most Amish men don’t say no to their wives’ purchase requests often. Married Amish women have access to all the creature comforts the church allows to make their lives as pleasant as possible.
When it comes to status, the benefits are just as clear. Amish life revolves around family, and nothing is higher status than a thriving family of your own. The Amish version of posting exotic vacation pictures on Instagram is showing up to a social function with your new baby. It’s the automatic center of attention for weeks, until a newer baby show up in the community. And the default topic of conversation is always a woman’s children and their growth and development. Young girls grow up dreaming of the day they can join those conversations, and old maids are always outsiders in a certain sense, pitied by everyone else for their misfortune.
Being an old maid means being poor, low status, pitied by other women, and destined to live with your parents until they pass, with your only bitter-sweet consolation being the role of aunt to your dozens of nieces and nephews and maid to your sisters and sisters-in-law through their many pregnancies. Getting married means access to a man’s income, a nice new house just the way you want it, a farm, and an automatic status boost as a mother and eventually grandmother who always has lots to contribute to the conversation at social events.
As you can imagine, the incentives strongly favor marriage from both directions. Men benefit through improved lifestyle, status, and access to sex. Women benefit through improved lifestyle, economic opportunity, and status in the social hierarchy.
Given that the selection pool for potential partners is limited, mostly to the local Amish community, or occasionally another Amish community if there’s some interaction through family ties or social events, assortative mating is the norm. Young people can be choosy, sure. But they already know most of the people in their potential mating pool, and have probably known those people for most of their lives. They have a pretty good idea how desirable they are to potential partners, and the girls especially have to think long and hard about turning down a suitor. Men are always the initiators of a relationship, and the risk of turning down an eligible man and then never getting another offer, ending up as a dreaded old maid, is always lurking in the back of their minds.
Besides that, both men and women have multiple ways to improve their spouse’s life. Women are much more than just sexual objects. Their domestic role actually raises their husband’s standard of living significantly, in a way he can’t access as a single man. And men are all valuable to women, both for resources and for status as a wife and mother. Even a very average husband or wife is a massive lifestyle boost over remaining single.
By now it should be pretty clear why marriage is almost universal among the Amish, and marriage at what most would consider a young age (19-23) is more common than not. And I haven’t even mentioned any religious teaching, because frankly I don’t think that’s a major force on an individual level. The religious beliefs shape the social and material landscape, and that landscape provides the practical incentives that cause people to make the choices they do. The fact that an Amish interpretation of the Bible encourages marriage and children is one layer removed from the reasons individual 20-year-old Amish men and women choose to get married.
I pointed out earlier that getting married and having a high birthrate, or even getting married young and having a high birthrate, are not exactly the same thing. Plenty of married couples today have one, two, or even no children, even if they got married young enough to have ten if they chose to do so. So why are the Amish different?
There’s the too-obvious answer: they don’t allow the use of contraceptives. Occam’s razor and all, but it deserves a bit more explanation. After all, the Catholic Church doesn’t allow the use of contraceptives either, and look how well that’s working out for them. Of course the enforcement mechanism doesn’t have the teeth among Catholics that it has among the Amish, but that’s not the whole story. If they were motivated enough, there’d be a way to space the children out more, maybe end up without quite so many, without anyone knowing. That doesn’t happen, because the contraceptive ban is a dead letter when couples want to have as many children as possible, which the Amish typically do.
Again, I’ll go back to incentives. What are the incentives to have children specifically, as many as possible, and not just get married and “plan for a family one day”?
For one, status. For both men and women, a large family is a marker of high status. Parents are respected and honored for doing a good job of raising well-adjusted children.
Children are also less of a financial burden for the Amish. Their children are raised well, but not in a financially intensive way that’s become expected today. They don’t have to buy a new car or SUV to fit the family, they don’t buy every child a boatload of expensive electronic gadgets every birthday and Christmas, they don’t have to pay for frequent vacations or college tuition, and they don’t have to eat out or pay for takeout or pay for childcare or a house cleaner since the wife is handling all those domestic roles herself. And the Amish don’t practice helicopter parenting, so children are much more free to play and amuse themselves without constant supervision from their parents. They don’t have to be driven to 17 different weekly structured activities. They have a farm to play on and shelves full of books to read and some toys to play with if the weather is bad, and that’s about it. And of course as the family grows, the older siblings do a large percentage of the housework and help with the younger children.
The older teenagers that are working outside the home typically give their earnings to their parents, but this basically offsets the cost of raising them, so it isn’t really an incentive to have larger families, just the removal of a disincentive.
The strongest real incentive, other than increased status and cultural inertia, that I observe for large families is that the children are the parents’ retirement plan. The Amish don’t work at jobs that offer pensions or benefits. They are exempt from paying into, but also ineligible to receive, Social Security benefits. The Social Security exemption was granted on the basis that the Amish don’t need government payments to support them in old age, because the family and community will do that. And they do.
How does this work out in practice? First, the Amish don’t practice “retirement” the way most people think of it. They teach that work is honorable and every able-bodied man should work to support his family and to help those in need. So as long as a man is physically able to work, he’ll be employed and supporting himself and his wife. And Amish women move directly from the role of mother to the role of grandmother. It’s not at all uncommon, in fact, for a woman’s first grandchild to be born before her last child is born. So plenty of Amish children are an aunt or uncle at birth, and have a niece or nephew older than they are. Grandmothers are extremely involved in helping their daughters and daughters-in-law with childcare, so they don’t often have a big stretch of free time after their children grow up and move out. And besides that, there are still the significant household responsibilities to attend to.
As a couple gets older and perhaps less able to handle everything on their own, they often move to the home of one of their grown children. Typically not into the home directly, but into what’s called a “dody haus” (grandpa house) which might be a small detached house on the same property, or a separate wing of the larger house, like an in-law suite. Here they’re able to live independently, help care for the grandchildren next door, and still be nearby so their children and grandchildren can give any care they may need in old age. If the couple has an unmarried “old maid” daughter, she’ll typically still be living with them and will be the primary caregiver.
If someone doesn’t have children to care for them, the Amish community will find a way to care for them. Some more distant relative or maybe surviving siblings will step in to help. But the expectation and the rule is that your children and grandchildren will care for you after you’re no longer able to care for yourself. Finding yourself growing old without family is an unfortunate and unpleasant situation, regardless how much the community may try to fill that role. Just as throughout earlier stages of life, social functions and social status revolve around children and family, and anyone without them will be incomplete as a person, something of an inevitable outsider to the joys of life. The best insurance against a lonely and uncomfortable old age is a large family, among which there are certain to be sufficient resources to care for you. Many elderly Amish people die with well over a hundred grandchildren and great-grandchildren, and spend their later years constantly surrounded by children and young people who deeply appreciate and respect them. Being taught and shown that respect toward their own grandparents from a young age is a strong incentive to aspire to the same status one day.
I’m not sure exactly where this fits, but I should point out somewhere that the Amish have an absolutely zero tolerance policy toward divorce. There are no legitimate grounds for divorce whatsoever, and anyone who initiates a divorce will be excommunicated from the church and shunned. If an Amish person’s spouse initiates divorce proceedings, they won’t cooperate with those proceedings in any way. If the divorce happens through the legal system without their consent anyway, they can remain a church member in good standing only by staying celibate as long as their spouse remains alive. The only acceptable second marriage is in the case of the death of a spouse. In those cases, a quick remarriage is the rule among widows and widowers with young children, since raising a family is seen as a job for a married couple, not a single person.
It’s hard to say exactly how this stance against divorce influences marriage and fertility. But it certainly limits exposure to the idea of divorce as a “solution” to marriage difficulties, and incentivizes couples to work things out for their own life satisfaction. And it dramatically reduces the financial risks men face in the modern marriage system, where the potential to lose not only their family, but also a significant portion of their material wealth, raises strong disincentives to marriage. The physical realities of married life versus single life in a more low-tech environment probably discourage divorce, but the added threat of complete social and familial ostracization eliminate it almost entirely.
Conclusion
This article is my attempt to provide some insight into the Amish culture that might help us understand the factors causing their unusually high fertility rate. I’ve titled it as part one, because I plan to follow up with some of my personal opinions on how these insights relate to the broader society. I think a lot of the proposed causes of and solutions to the global demographic collapse are completely incorrect, and my opinion is based heavily on my observation of Amish culture. That will be the focus of part two of this article.
Feel free to comment and post questions. My biggest challenge in writing this article is the fact that I take my familiarity with Amish culture for granted to some degree, so I struggled to choose which points are relevant to understanding the culture for an outsider. I’m sure I skipped over plenty of important details that may leave readers feeling confused, so I’ll do my best to answer any questions you post, and update the article with pertinent information I missed.
-
-
 @ c9badfea:610f861a
2025-05-24 12:55:17
@ c9badfea:610f861a
2025-05-24 12:55:17Before you post a message or article online, let the LLM check if you are leaking any personal information using this prompt:
Analyze the following text to identify any Personally Identifiable Information (PII): <Your Message>Replace
<Your Message>with your textIf no PII is found, continue by modifying your message to detach it from your personality. You can use any of the following prompts (and further modify it if necessary).
Prompt № 1 - Reddit-Style
Convert the message into a casual, Reddit-style post without losing meaning. Split the message into shorter statements with the same overall meaning. Here is the message: <Your Message>Prompt № 2 - Advanced Modifications
``` Apply the following modifications to the message: - Rewrite it in lowercase - Use "u" instead of "you" - Use "akchoaly" instead of "actually" - Use "hav" instead of "have" - Use "tgat" instead of "that" - Use comma instead of period - Use British English grammar
Here is the message:
``` Prompt № 3 - Neutral Tone
Rewrite the message to correct grammar errors, and ensure the tone is neutral and free of emotional language: <Your Message>Prompt № 4 - Cross Translation Technique
Translate the message into Chinese, then translate the resulting Chinese text back into English. Provide only the final English translation. Here is the message: <Your Message>Check the modified message and send it.
ℹ️ You can use dialects to obfuscate your language further. For example, if you are from the US, you can tell the LLM to use British grammar and vice versa.
⚠️ Always verify the results. Don't fully trust an LLM.
-
 @ 90c656ff:9383fd4e
2025-05-24 12:11:01
@ 90c656ff:9383fd4e
2025-05-24 12:11:01Since its creation, Bitcoin has marked a turning point in the digital money revolution—but its evolution didn’t stop at the original concept of decentralized transactions. Over the years, new technological solutions have been developed to expand its capabilities, making it more efficient and versatile. Among these innovations, smart contracts and the Lightning Network stand out, enabling increased functionality and scalability of the network, and ensuring a faster, cheaper, and more accessible system.
Smart contracts on Bitcoin
Smart contracts are programs that automatically execute certain actions when predefined conditions are met. Although the concept is more commonly associated with other networks, Bitcoin also supports smart contracts, especially through upgrades like Taproot.
- Smart contracts on Bitcoin enable functionalities such as:
01 - Conditional payments: Transactions that are only completed if certain rules are met, such as multi-signatures or specific time conditions.
02 - Advanced fund management: Use of multi-signature wallets, where different parties must approve a transaction before it is processed.
03 - Enhanced privacy: With the Taproot upgrade, smart contracts can be more efficient and indistinguishable from regular transactions, improving privacy across the network.
Although smart contracts on Bitcoin are simpler than those on other platforms, this simplicity is a strength—it preserves the network's security and robustness by avoiding complex vulnerabilities.
Lightning Network: scalability and instant transactions
One of the biggest challenges Bitcoin faces is scalability. Since the original network was designed to prioritize security and decentralization, transaction speed can be limited during periods of high demand. To address this issue, the Lightning Network was created—a second-layer solution that enables near-instant transactions with extremely low fees.
The Lightning Network works by creating payment channels between users, allowing them to conduct multiple transactions off-chain and recording only the final balance on the main Bitcoin blockchain or timechain. Key advantages include:
01 - Speed: Transactions are completed in milliseconds, making Bitcoin more suitable for daily payments.
02 - Low fees: Since transactions occur off-chain, fees are minimal, allowing for viable microtransactions.
03 - Network decongestion: By moving many transactions to the Lightning Network, Bitcoin’s main chain becomes more efficient and less congested.
In summary, Bitcoin continues to evolve technologically to meet the demands of a global financial system. Smart contracts increase its functionality, offering greater flexibility and security in transactions. The Lightning Network improves scalability, making Bitcoin faster and more practical for everyday use. With these innovations, Bitcoin remains at the forefront of the financial revolution, proving that despite its initial limitations, it continues to adapt and grow as a truly decentralized and global monetary system.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ 90c656ff:9383fd4e
2025-05-24 12:06:36
@ 90c656ff:9383fd4e
2025-05-24 12:06:36Throughout history, money has always been under the control of central authorities, such as governments and banks. These intermediaries have set the rules of the financial system, controlled the issuance of currency, and overseen transactions. However, with the emergence of Bitcoin, a new paradigm began to take shape: decentralized money. This transformation represents a profound shift in how people store and transfer value, challenging the traditional financial model.
- The traditional model: centralized money
01 - Dependence on intermediaries: To carry out transactions, people rely on banks, governments, and other regulatory entities.
02 - Inflation and devaluation: Central banks can print money endlessly, often leading to a loss in purchasing power.
03 - Censorship and restrictions: Access to money can be denied for political, bureaucratic, or institutional reasons, limiting individuals’ financial freedom.
Despite being the dominant model for centuries, the centralized system has shown its vulnerabilities through numerous economic and political crises. It was in this context that Bitcoin emerged as an innovative alternative.
- The revolution of decentralized money
01 - Elimination of intermediaries: Transactions can be made directly between users, without the need for banks or financial companies.
02 - Limited and predictable supply: Bitcoin has a fixed cap of 21 million units, preventing the inflation caused by excessive money printing.
03 - Censorship resistance: No entity can block or prevent transactions, ensuring full financial freedom.
04 - Self-custody: Each user can hold their own funds without relying on a bank or any other institution.
This paradigm shift has a significant impact not only on the financial system but also on how people interact with money and protect their wealth.
Challenges and opposition to financial decentralization
The transition to a decentralized financial system faces several challenges, the main one being resistance from traditional institutions. Banks and governments see Bitcoin as a threat to their control over money and seek to regulate or limit its adoption.
There are also technical and educational barriers. Many people still do not fully understand how Bitcoin works, which can hinder its adoption. However, as more people become aware of the benefits of decentralized money, its use is likely to grow.
In summary, the shift from a centralized financial system to a decentralized one represents one of the most significant transformations of the digital era. Bitcoin leads this movement by offering a censorship-resistant, transparent, and accessible alternative. Despite opposition from the traditional system, the decentralization of money continues to gain momentum, providing greater autonomy and financial freedom to people around the world. This revolution is not just technological, but also social and economic—redefining the way the world understands and uses money.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ b1ddb4d7:471244e7
2025-05-24 11:00:40
@ b1ddb4d7:471244e7
2025-05-24 11:00:40The upcoming Bitcoin 2025 conference, scheduled from May 27–29 at the Venetian Conference Center in Las Vegas, is set to make history with an official attempt to break the GUINNESS WORLD RECORDS® title for the most Bitcoin point-of-sale transactions in an eight-hour period.
Organized by BTC Inc, the event will showcase Bitcoin’s evolution from a digital capital asset to a practical medium of exchange, leveraging the latest advancements in payment technology.
Tap-to-Pay with Lightning-Ready Bolt Cards
To facilitate this record-setting attempt, 4,000 Lightning-ready Bolt Cards will be distributed to conference attendees.
— Uncle Rockstar Developer (@r0ckstardev) May 15, 2025
These NFC-enabled cards allow users to make instant, contactless Bitcoin payments at vendor booths throughout the expo-no apps or QR codes required, just a simple tap.
The cards are available in four collectible designs, each featuring a prominent figure in Bitcoin’s history: Senator Cynthia Lummis, Michael Saylor, Satoshi Nakamoto, and Jack Dorsey.
Each attendee will receive a randomly assigned card, making them both functional and collectible souvenirs.
Senator Lummis: A Playful Provocation
Notably, one of the card designs features Senator Cynthia Lummis with laser eyes-a playful nod to her reputation as a leading Bitcoin advocate in US politics.
While Lummis is known for her legislative efforts to promote Bitcoin integration, she has publicly stated she prefers to “spend dollars and save Bitcoin,” viewing BTC as a long-term store of value rather than a daily currency.
The choice to feature her on the Bolt Card, could be suggested by Rockstar Dev of the BTC Pay Server Foundation, perhaps a lighthearted way to highlight the ongoing debate about Bitcoin’s role in everyday payments.
Nothing cracks me up quite like a senator that wants the US to buy millions of Bitcoin use dollars to buy a beer at a Bitcoin bar.
This is how unserious some of you are. pic.twitter.com/jftIEggmip
— Magoo PhD (@HodlMagoo) April 4, 2025
How Bolt Cards and the Lightning Network Work
Bolt Cards are physical cards equipped with NFC (Near Field Communication) technology, similar to contactless credit or debit cards. When linked to a compatible Lightning wallet, they enable users to make Bitcoin payments over the Lightning Network by simply tapping the card at a point-of-sale terminal.
The Lightning Network is a second-layer protocol built on top of Bitcoin, designed to facilitate instant, low-cost transactions ideal for everyday purchases.
This integration aims to make Bitcoin as easy to use as traditional payment methods, eliminating the need for QR code scanning or mobile apps.
A Showcase for Bitcoin’s Real-World Usability
With over 30,000 attendees, 300 exhibitors, and 500 speakers expected, the Bitcoin 2025 conference is poised to be the largest Bitcoin event of the year-and potentially the most transactional.
The event will feature on-site activations such as the Official Bitcoin Magazine Store, where all merchandise will be available at a 21% discount for those paying with Bitcoin via the Lightning Network-a nod to Bitcoin’s 21 million coin supply limit.
By deeply integrating Lightning payments into the conference experience, organizers hope to demonstrate Bitcoin’s readiness for mainstream commerce and set a new benchmark for its practical use as a currency.
Conclusion
The Guinness World Record attempt at Bitcoin 2025 is more than a publicity stunt-it’s a bold demonstration of Bitcoin’s technological maturity and its potential to function as a modern, everyday payment method.
Whether or not the record is set, the event will serve as a milestone in the ongoing journey to make Bitcoin a truly global, user-friendly currency
-
 @ 7460b7fd:4fc4e74b
2025-05-17 08:26:13
@ 7460b7fd:4fc4e74b
2025-05-17 08:26:13背景:WhatsApp的号码验证与运营商合作关系
作为一款基于手机号码注册的即时通信应用,WhatsApp的账号验证严重依赖全球电信运营商提供的短信或电话服务。这意味着,当用户注册或在新设备登录WhatsApp时,WhatsApp通常会向用户的手机号码发送SMS短信验证码或发起语音电话验证。这一流程利用了传统电信网络的基础设施,例如通过SS7(信令系统7)协议在全球范围内路由短信和电话securityaffairs.com。换句话说,WhatsApp把初始账户验证的安全性建立在电信运营商网络之上。然而,这种依赖关系也带来了隐患:攻击者可以利用电信网络的漏洞来拦截验证码。例如,研究人员早在2016年就演示过利用SS7协议漏洞拦截WhatsApp和Telegram的验证短信,从而劫持用户账户的攻击方法securityaffairs.com。由于SS7协议在全球范围内连接各国运营商,一个运营商的安全缺陷或恶意行为都可能被不法分子利用来获取他网用户的短信验证码securityaffairs.com。正因如此,有安全专家指出,仅依赖短信验证不足以保障账户安全,WhatsApp等服务提供商需要考虑引入额外机制来核实用户身份securityaffairs.com。
除了技术漏洞,基于电信运营商的验证还受到各地政策和网络环境影响。WhatsApp必须与全球各地运营商“合作”,才能将验证码送达到用户手机。然而这种“合作”在某些国家可能并不顺畅,典型例子就是中国。在中国大陆,国际短信和跨境电话常受到严格管控,WhatsApp在发送验证码时可能遭遇拦截或延迟sohu.com。因此,理解WhatsApp在中国的特殊联网和验证要求,需要将其全球验证机制与中国的电信政策和网络审查环境联系起来。下文将深入探讨为什么在中国使用WhatsApp进行号码验证时,必须开启蜂窝移动数据,并分析其中的技术逻辑和政策因素。
中国环境下的特殊问题:为何必须开启蜂窝数据?
中国的网络审查与封锁: WhatsApp自2017年起就在中国大陆遭遇严格封锁。起初,WhatsApp在华的服务受到**“GFW”(防火长城)**的部分干扰——例如曾一度只能发送文本消息,语音、视频和图片消息被封锁theguardian.com。到2017年下半年,封锁升级,很多用户报告在中国完全无法使用WhatsApp收发任何消息theguardian.com。中国官方将WhatsApp与Facebook、Telegram等西方通信平台一同屏蔽,视作对国家网络主权的挑战theguardian.com。鉴于此,在中国境内直接访问WhatsApp的服务器(无论通过Wi-Fi还是本地互联网)都会被防火长城所阻断。即使用户收到了短信验证码,WhatsApp客户端也无法在没有特殊连接手段的情况下与服务器完成验证通信。因此,单纯依赖Wi-Fi等本地网络环境往往无法完成WhatsApp的注册或登陆。很多用户经验表明,在中国使用WhatsApp时需要借助VPN等工具绕过审查,同时尽可能避免走被审查的网络路径sohu.com。
强制Wi-Fi热点与连接策略: 除了国家级的封锁,用户所连接的局域网络也可能影响WhatsApp验证。许多公共Wi-Fi(如机场、商场)采取强制门户认证(captive portal),用户需登录认证后才能上网。对此,WhatsApp在客户端内置了检测机制,当发现设备连入这类强制Wi-Fi热点而无法访问互联网时,会提示用户忽略该Wi-Fi并改用移动数据faq.whatsapp.com。WhatsApp要求对此授予读取Wi-Fi状态的权限,以便在检测到被拦截时自动切换网络faq.whatsapp.com。对于中国用户来说,即便所连Wi-Fi本身联网正常,由于GFW的存在WhatsApp依然可能视之为“不通畅”的网络环境。这也是WhatsApp官方指南中强调:如果Wi-Fi网络无法连接WhatsApp服务,应直接切换到手机的移动数据网络faq.whatsapp.com。在中国,由于本地宽带网络对WhatsApp的封锁,蜂窝数据反而成为相对可靠的通道——尤其在搭配VPN时,可以避开本地ISP的审查策略,实现与WhatsApp服务器的通信sohu.com。
国际短信的运营商限制: 使用移动数据还有助于解决短信验证码接收难题。中国的手机运营商出于防垃圾短信和安全考虑,默认对国际短信和境外来电进行一定限制。许多中国用户发现,注册WhatsApp时迟迟收不到验证码短信,原因可能在于运营商将来自国外服务号码的短信拦截或过滤sohu.com。例如,中国移动默认关闭国际短信接收,需要用户主动发送短信指令申请开通sohu.com。具体而言,中国移动用户需发送文本“11111”到10086(或10085)来开通国际短信收发权限;中国联通和电信用户也被建议联系运营商确认未屏蔽国际短信sohu.com。若未进行这些设置,WhatsApp发送的验证码短信可能根本无法抵达用户手机。在这种情况下,WhatsApp提供的备用方案是语音电话验证,即通过国际电话拨打用户号码并播报验证码。然而境外来电在中国也可能遭到运营商的安全拦截,特别是当号码被认为可疑时zhuanlan.zhihu.com。因此,中国用户经常被建议开启手机的蜂窝数据和漫游功能,以提高验证码接收的成功率sohu.com。一方面,开启数据漫游意味着用户准备接受来自境外的通信(通常也包含短信/电话);另一方面,在数据联网的状态下,WhatsApp可以尝试通过网络直接完成验证通信,从而减少对SMS的依赖。
移动数据的网络路径优势: 在实际案例中,一些中国WhatsApp用户报告仅在开启蜂窝数据的情况下才能完成验证。这可能归因于蜂窝网络和宽带网络在国际出口上的差异。中国移动、联通等运营商的移动数据可能走与宽带不同的网关路由,有时对跨境小流量的拦截相对宽松。此外,WhatsApp在移动数据环境中可以利用一些底层网络特性。例如,WhatsApp可能通过移动网络发起某些专用请求或利用运营商提供的号码归属地信息进行辅助验证(虽然具体实现未公开,但这是业界讨论的可能性)。总之,在中国特殊的网络环境下,开启蜂窝数据是确保WhatsApp验证流程顺利的重要一步。这一步不仅是为了基本的互联网连接,也是为了绕开种种对国际短信和应用数据的拦截限制,从而与WhatsApp的全球基础设施建立必要的通讯。
PDP Context与IMSI:移动网络验证的技术细节
要理解为什么移动数据对WhatsApp验证如此关键,有必要了解移动通信网络中的一些技术细节,包括PDP Context和IMSI的概念。
PDP Context(分组数据协议上下文): 当手机通过蜂窝网络使用数据(如4G/5G上网)时,必须先在运营商核心网中建立一个PDP上下文。这实际上就是申请开启一个数据会话,运营商将为设备分配一个IP地址,并允许其通过移动核心网访问互联网datascientest.com。PDP上下文包含了一系列参数(例如APN接入点名称、QoS等级等),描述该数据会话的属性datascientest.comdatascientest.com。简单来说,激活蜂窝数据就意味着创建了PDP上下文,设备获得了移动网络网关分配的IP地址,可以收发数据包。对于WhatsApp验证而言,只有在建立数据连接后,手机才能直接与WhatsApp的服务器交换数据,例如提交验证码、完成加密密钥协商等。如果仅有Wi-Fi而蜂窝数据关闭,且Wi-Fi环境无法连通WhatsApp服务器,那么验证过程将陷入停滞。因此,在中国场景下,开启蜂窝数据(即建立PDP数据通路)是WhatsApp客户端尝试绕过Wi-Fi限制、直接通过移动网络进行验证通信的前提faq.whatsapp.comsohu.com。值得一提的是,PDP Context的建立也表明手机在运营商网络上处于活跃状态,这对于某些验证机制(比如后述的闪信/闪呼)来说至关重要。
IMSI与MSISDN: IMSI(国际移动用户标识)和MSISDN(移动用户号码,即手机号码)是运营商网络中两个密切相关但不同的标识。IMSI是存储在SIM卡上的一串唯一数字,用于在移动网络中标识用户身份netmanias.com。当手机接入网络时,它向运营商提供IMSI以进行鉴权,运营商据此知道“是哪张SIM”的请求netmanias.com。而MSISDN则是我们平常说的手机号,用于在语音通话和短信路由中定位用户,也存储在运营商的HLR/HSS数据库中netmanias.com。运营商通过IMSI<->MSISDN的对应关系,将来自全球的短信/电话正确路由到用户手机上。WhatsApp的验证短信或电话本质上就是通过目标号码(MSISDN)寻找所属运营商网络,由该网络根据IMSI定位用户终端。一般情况下,WhatsApp应用并不直接接触IMSI这种信息,因为IMSI属于运营商网络的内部标识。然而,IMSI的存在仍然对安全产生影响。例如,**SIM卡交换(SIM Swap)**欺诈发生时,攻击者获得了受害者号码的新SIM卡,新SIM卡会有不同的IMSI,但MSISDN保持原号码不变。运营商会将原号码映射到新的IMSI,这样验证码短信就发送到了攻击者手中的SIM上。对WhatsApp而言,除非有机制检测IMSI变动,否则无法察觉用户号码背后的SIM已被盗换。部分应用在检测到SIM变化时会提示用户重新验证,这需要读取设备的IMSI信息进行比对。然而,在现代智能手机中,获取IMSI通常需要特殊权限,WhatsApp并未明确说明它有此类检测。因此,从WhatsApp角度,IMSI更多是网络侧的概念,但它提醒我们:电信级身份验证依赖于SIM的有效性。只有当正确的IMSI在网络注册、并建立了PDP数据上下文时,WhatsApp的后台服务才能确认该SIM对应的号码目前“在线”,进而可靠地发送验证信号(短信或电话)到该设备。
移动网络的信号辅助验证: 有观点认为,一些OTT应用可能利用移动网络提供的附加服务来辅助号码验证。例如,某些运营商提供号码快速验证API,当应用检测到设备在移动数据网络中时,可以向特定地址发起请求,由运营商返回当前设备的号码信息(通常通过已经建立的PDP通道)。Google等公司在部分国家与运营商合作过类似服务,实现用户免输入验证码自动完成验证。但就WhatsApp而言,没有公开证据表明其使用了运营商提供的自动号码识别API。即便如此,WhatsApp鼓励用户保持移动网络在线的做法,隐含的意义之一可能是:当手机处于蜂窝网络且数据畅通时,验证码通过率和验证成功率都会显著提升。这既包括了物理层面短信、电话能否送达,也涵盖了数据层面应用和服务器能否互通。
Flash Call机制:WhatsApp验证的新方案
针对传统SMS验证码容易被拦截、延迟以及用户体验不佳的问题,WhatsApp近年来引入了一种Flash Call(闪呼)验证机制fossbytes.com。所谓闪呼,即应用在用户验证阶段向用户的手机号发起一个非常短暂的来电:用户无需真正接听,WhatsApp会自动结束这通电话,并根据通话记录来确认是否拨通fossbytes.com。
原理与流程: 当用户选择使用闪呼验证(目前主要在Android设备上可用),WhatsApp会请求权限访问用户的通话记录fossbytes.com。随后应用拨打用户的号码,一般是一个预先设定的特定号码或号码段。由于WhatsApp后台知道它拨出的号码及通话ID,只要该未接来电出现在用户手机的通话日志中,应用即可读取并匹配最后一通来电的号码是否符合验证要求,从而确认用户持有这个号码fossbytes.com。整个过程用户无需手动输入验证码,验证通话在数秒内完成。相比6位数字短信验证码需要用户在短信和应用间切换输入,闪呼方式更加快捷无缝fossbytes.com。
优缺点分析: 闪呼验证的优势在于速度快且避免了SMS可能的延迟或拦截。一些分析指出闪呼将成为取代SMS OTP(一次性密码)的新趋势,Juniper Research预测2022年用于验证的闪呼次数将从2021年的六千万猛增到五十亿次subex.comglobaltelcoconsult.com。对于WhatsApp这样全球用户庞大的应用,闪呼可以节约大量SMS网关费用,并绕开部分运营商对国际SMS的限制。然而,闪呼也有局限:fossbytes.com首先,iOS设备由于系统安全限制,应用无法访问通话记录,因此iPhone上无法使用闪呼验证fossbytes.com。这意味着苹果用户仍需使用传统短信验证码。其次,为实现自动匹配来电号码,用户必须授予读取通话记录的权限,这在隐私上引发一些担忧fossbytes.comfossbytes.com。WhatsApp声称不会将通话记录用于验证以外的用途,号码匹配也在本地完成fossbytes.com,但考虑到母公司Meta的隐私争议,部分用户依然顾虑。第三,闪呼验证依赖语音通话路线,同样受制于电信网络质量。如果用户所处网络无法接通国际来电(比如被运营商拦截境外短振铃电话),闪呼也无法成功。此外,从运营商角度看,闪呼绕过了A2P短信计费,可能侵蚀短信营收,一些运营商开始研究识别闪呼流量的策略wholesale.orange.com。总体而言,闪呼机制体现了WhatsApp希望减轻对短信依赖的努力,它在许多国家提升了验证体验,但在中国等特殊环境,其效果仍取决于本地语音网络的开放程度。值得注意的是,中国运营商对于境外电话,尤其是这种**“零响铃”未接来电**也有防范措施,中国电信和联通用户就被建议如需接收海外来电验证,应联系客服确保未拦截海外来电hqsmartcloud.com。因此,即便WhatsApp支持闪呼,中国用户若未开启移动语音漫游或运营商许可,仍然难以通过此途径完成验证。
与SIM Swap安全性的关系: 从安全角度看,闪呼并未实质提升抵御SIM交换攻击的能力。如果攻击者成功将受害者的号码转移至自己的SIM卡上(获取新IMSI),那么无论验证码以短信还是闪呼方式发送,都会到达攻击者设备。闪呼机制能防御的是部分恶意拦截短信的行为(如恶意网关或木马读取短信),但对社工换卡没有太大帮助。WhatsApp早已提供两步验证(即设置6位PIN码)供用户自行启用,以防号码被他人重新注册时需要额外密码。然而大量用户未开启该功能。因此,闪呼更多是从用户体验和成本出发的改良,而非针对高级别攻击的防护机制。正如前文所述,真正要防御SIM Swap和SS7漏洞等系统性风险,依赖运营商的号码验证本身就是薄弱环节,需要引入更高级的身份认证手段。
SIM卡交换攻击的风险与运营商信任问题
WhatsApp和Telegram一类基于手机号认证的应用普遍面临一个安全挑战:手机号码本身并非绝对安全的身份凭证。攻击者可以通过一系列手段取得用户的号码控制权,其中SIM交换(SIM Swap)是近年高发的欺诈手法。SIM Swap通常由不法分子冒充用户,诱骗或贿赂运营商客服将目标号码的服务转移到攻击者的新SIM卡上keepnetlabs.com。一旦成功,所有发往该号码的短信和电话都转由攻击者接收,原机主的SIM卡失效。对于依赖短信/电话验证的应用来说,这意味着攻击者可以轻易获取验证码,从而重置账户并登录。近年来全球SIM Swap案件呈上升趋势,许多在线服务的账号被此攻破rte.ie。
WhatsApp并非未知晓此风险。事实上,WhatsApp在其帮助中心和安全博客中多次提醒用户开启两步验证PIN,并强调绝不向他人透露短信验证码。然而,从系统设计上讲,WhatsApp仍将信任根基放在运营商发送到用户手机的那串数字验证码上。一旦运营商端的安全被绕过(无论是内部员工作恶、社工欺诈,还是SS7网络被黑客利用securityaffairs.com),WhatsApp本身无法辨别验证码接收者是否是真正的用户。正如安全研究所Positive Technologies指出的那样,目前主要的即时通讯服务(包括WhatsApp和Telegram)依赖SMS作为主要验证机制,这使得黑客能够通过攻击电信信令网络来接管用户账户securityaffairs.com。换言之,WhatsApp被迫信任每一个参与短信/电话路由的运营商,但这个信任链条上任何薄弱环节都可能遭到利用securityaffairs.com。例如,在SIM Swap攻击中,运营商本身成为被欺骗的对象;而在SS7定位拦截攻击中,全球互联的电信网成为攻击面。在中国的场景下,虽然主要威胁来自审查而非黑客,但本质上仍是WhatsApp无法完全掌控电信网络这一事实所导致的问题。
应对这些风险,WhatsApp和Telegram等采用了一些弥补措施。除了提供用户自行设定的二次密码,两者也开始探索设备多因子的概念(如后文Telegram部分所述,利用已有登录设备确认新登录)。然而,对绝大多数首次注册或更换设备的用户来说,传统的短信/电话验证仍是唯一途径。这就是为什么在高安全需求的行业中,SMS OTP正逐渐被视为不充分securityaffairs.com。监管机构和安全专家建议对涉敏感操作采用更强验证,如专用身份应用、硬件令牌或生物识别等。WhatsApp作为大众通信工具,目前平衡了易用性与安全性,但其依赖电信运营商的验证模式在像中国这样特殊的环境下,既遇到政策阻碍,也隐藏安全短板。这一点对于决策制定者评估国外通信应用在华风险时,是一个重要考量:任何全球运营商合作机制,在中国境内都可能因为**“最后一公里”由中国运营商执行**而受到影响。无论是被拦截信息还是可能的监控窃听,这些风险都源自于底层通信网的控制权不在应用服务商手中。
Telegram登录机制的比较
作为对比,Telegram的账号登录机制与WhatsApp类似,也以手机号码为主要身份标识,但在具体实现上有一些不同之处。
多设备登录与云端代码: Telegram从设计上支持多设备同时在线(手机、平板、PC等),并将聊天内容储存在云端。这带来的一个直接好处是:当用户在新设备上登录时,Telegram会优先通过已登录的其他设备发送登录验证码。例如,用户尝试在电脑上登录Telegram,Telegram会在用户手机上的Telegram应用里推送一条消息包含登录码,而不是立即发短信accountboy.comaccountboy.com。用户只需在新设备输入从老设备上收到的代码即可完成登录。这种机制确保了只要用户至少有一个设备在线,就几乎不需要依赖运营商短信。当然,如果用户当前只有一部新设备(例如换了手机且旧设备不上线),Telegram才会退而求其次,通过SMS发送验证码到手机号。同时,Telegram也允许用户选择语音电话获取验证码,类似于WhatsApp的语音验证。当用户完全无法收到SMS时(比如在中国这种场景),语音呼叫常常比短信更可靠seatuo.com。
两步验证密码: 与WhatsApp一样,Telegram提供可选的两步验证密码。当启用此功能后,即使拿到短信验证码,仍需输入用户设置的密码才能登录账户quora.com。这对抗SIM Swap等攻击提供了另一层防线。不过需要指出,如果用户忘记了设置的Telegram密码且没有设置信任邮箱,可能会永久失去账号访问,因此开启该功能在中国用户中接受度一般。
登录体验与安全性的取舍: Telegram的登录流程在用户体验上更加灵活。多设备下无需每次都收验证码,提高了便利性。但从安全角度看,这种“信任已有设备”的做法也有隐患:如果用户的某个设备落入他人之手并未及时登出,那么该人有可能利用该设备获取新的登录验证码。因此Telegram会在应用中提供管理活动会话的功能,用户可随时查看和撤销其它设备的登录状态telegram.org。总体而言,Telegram和WhatsApp在初始注册环节同样依赖短信/电话,在这一点上,中国的网络环境对两者影响相似:Telegram在中国同样被全面封锁,需要VPN才能使用,其短信验证码发送也会受到运营商限制。另外,Telegram曾在2015年因恐怖分子利用该平台传递信息而被中国当局重点关注并屏蔽,因此其国内可达性甚至比WhatsApp更低。许多中国用户实际使用Telegram时,通常绑定国外号码或通过海外SIM卡来收取验证码,以绕开国内运营商的限制。
差异总结: 简而言之,Telegram在登录验证机制上的主要优势在于已有会话协助和云端同步。这使得老用户换设备时不依赖国内短信通道即可登录(前提是原设备已登录并可访问)。WhatsApp直到最近才推出多设备功能,但其多设备模式采用的是端到端加密设备链路,需要主手机扫码授权,而非像Telegram那样用账号密码登录其它设备。因此WhatsApp仍然强绑定SIM卡设备,首次注册和更换手机号时逃不开运营商环节。安全方面,两者的SMS验证所面临的系统性风险(如SS7攻击、SIM Swap)并无本质区别,都必须仰仗运营商加强对核心网络的保护,以及用户自身启用附加验证措施securityaffairs.comkeepnetlabs.com。
结论
对于希望在中国使用WhatsApp的用户来说,“开启蜂窝数据”这一要求背后体现的是技术与政策交织的复杂现实。一方面,蜂窝数据承载着WhatsApp与其全球服务器通信的关键信道,在中国的受限网络中提供了相对可靠的出路faq.whatsapp.comsohu.com。另一方面,WhatsApp的号码验证机制深深植根于传统电信体系,必须经由全球运营商的“协作”才能完成用户身份确认securityaffairs.com。而在中国,这种协作受到防火长城和运营商政策的双重阻碍:国际短信被拦截、国际数据被阻断。为克服这些障碍,WhatsApp既采取了工程上的应对(如检测强制Wi-Fi并提示使用移动网络faq.whatsapp.com),也引入了诸如闪呼验证等新方案以减少对短信的依赖fossbytes.com。但从根本上说,只要注册流程离不开手机号码,这种与电信运营商的捆绑关系就无法割舍。由此带来的安全问题(如SIM Swap和信令网络漏洞)在全球范围内敲响警钟securityaffairs.comkeepnetlabs.com。
对于从事安全研究和政策评估的人士,这篇分析揭示了WhatsApp在中国遇到的典型困境:技术系统的全球化与监管环境的本地化冲突。WhatsApp全球统一的验证框架在中国水土不服,不得不通过额外的设置和手段来“曲线救国”。这既包括让用户切换网络、配置VPN等绕过审查,也包括思考未来是否有必要采用更安全独立的验证方式。相比之下,Telegram的机制给出了一种启示:灵活运用多设备和云服务,至少在一定程度上降低对单一短信渠道的依赖。然而,Telegram自身在中国的处境表明,再优雅的技术方案也难以直接对抗高强度的网络封锁。最终,无论是WhatsApp还是Telegram,要想在受限环境下可靠运作,都需要技术与政策的双管齐下:一方面提高验证与登录的安全性和多样性,另一方面寻求运营商和监管层面的理解与配合。
综上所述,WhatsApp要求中国用户开启蜂窝数据并非偶然的臆想,而是其全球运营商合作验证机制在中国受阻后的务实选择。这一要求折射出移动通信应用在跨境运营中面临的挑战,也提醒我们在设计安全策略时必须考虑底层依赖的信任假设。对于个人用户,最实际的建议是在使用此类应用时提前了解并遵循这些特殊设置(如开通国际短信、启用数据漫游),并善用应用自身的安全功能(如两步验证)来保护账户免遭社工和网络攻击keepnetlabs.com。对于监管和运营商,则有必要权衡安全审查与用户便利之间的平衡,在可控范围内为可信的全球服务留出技术通道。在全球通信愈加融合的时代,WhatsApp的中国验证问题或许只是一个缩影,背后涉及的既有网络安全考量,也有数字主权与国际合作的议题,值得持续深入研究和关注。
faq.whatsapp.comfossbytes.comtheguardian.comsecurityaffairs.comsecurityaffairs.comkeepnetlabs.comdatascientest.comnetmanias.comsohu.comsohu.com
-
 @ b1ddb4d7:471244e7
2025-05-24 11:00:38
@ b1ddb4d7:471244e7
2025-05-24 11:00:38Flash, an all-in-one Bitcoin payment platform, has announced the launch of Flash 2.0, the most intuitive and powerful Bitcoin payment solution to date.
With a completely redesigned interface, expanded e-commerce integrations, and a frictionless onboarding process, Flash 2.0 makes accepting Bitcoin easier than ever for businesses worldwide.
 We did the unthinkable!
We did the unthinkable! Website monetization used to be super complicated.
"Buy me a coffee" — But only if we both have a bank account.
WHAT IF WE DON'T?
Thanks to @paywflash and bitcoin, it's just 5 CLICKS – and no banks!
 Start accepting donations on your website… pic.twitter.com/uwZUrvmEZ1
Start accepting donations on your website… pic.twitter.com/uwZUrvmEZ1— Flash • The Bitcoin Payment Gateway (@paywflash) May 13, 2025
Accept Bitcoin in Three Minutes
Setting up Bitcoin payments has long been a challenge for merchants, requiring technical expertise, third-party processors, and lengthy verification procedures. Flash 2.0 eliminates these barriers, allowing any business to start accepting Bitcoin in just three minutes, with no technical set-up and full control over their funds.
The Bitcoin Payment Revolution
The world is witnessing a seismic shift in finance. Governments are backing Bitcoin funds, major companies are adding Bitcoin to their balance sheets, and political figures are embracing it as the future of money. Just as Stripe revolutionized internet payments, Flash is now doing the same for Bitcoin. Businesses that adapt today will gain a competitive edge in a rapidly evolving financial landscape.
With Bitcoin adoption accelerating, consumers are looking for places to spend it. Flash 2.0 ensures businesses of all sizes can seamlessly accept Bitcoin and position themselves at the forefront of this financial revolution.
All-in-One Monetization Platform
More than just a payment gateway, Flash 2.0 is a complete Bitcoin monetization suite, providing multiple ways for businesses to integrate Bitcoin into their operations. Merchants can accept payments online and in-store, content creators can monetize with donations and paywalls, and freelancers can send instant invoices via payment links.
For example, a jewelry designer selling products on WooCommerce can now integrate Flash for online payments, use Flash’s Point-of-Sale system at trade shows, enable Bitcoin donations for her digital artwork, and lock premium content behind Flash Paywalls. The possibilities are endless.
E-Commerce for Everyone
With built-in integrations for Shopify, WooCommerce, and soon Wix and OpenCart, Flash 2.0 enables Bitcoin payments on 95% of e-commerce stores worldwide. Businesses can now add Bitcoin as a payment option in just a few clicks—without needing developers or external payment processors.
And for those looking to start selling, Flash’s built-in e-commerce features allow users to create online stores, showcase products, and manage payments seamlessly.
No Middlemen, No Chargebacks, No Limits
Unlike traditional payment platforms, Flash does not hold or process funds. Businesses receive Bitcoin directly, instantly, and securely. There are no chargebacks, giving merchants full control over refunds and eliminating fraud. Flash also remains KYC-free, ensuring a seamless experience for businesses and customers alike.
A Completely Redesigned Experience
“The world is waking up to Bitcoin. Just like the internet revolutionized commerce, Bitcoin is reshaping finance. Businesses need solutions that are simple, efficient, and truly decentralized. Flash 2.0 is more than just a payment processor—it’s a gateway to the future of digital transactions, putting financial power back into the hands of businesses.”
— Pierre Corbin, CEO at Flash.
Flash 2.0 introduces a brand-new user interface, making it easier than ever to navigate, set up payments, and manage transactions. With an intuitive dashboard, streamlined checkout, and enhanced mobile compatibility, the platform is built for both new and experienced Bitcoin users.
About Flash
Flash is an all-in-one Bitcoin payment platform that empowers businesses, creators, and freelancers to accept, manage, and grow with Bitcoin. With a mission to make Bitcoin payments accessible to everyone, Flash eliminates complexity and gives users full control over their funds.
To learn more or get started, visit www.paywithflash.com.
Press Contact:
Julien Bouvier
Head of Marketing
+3360941039 -
 @ b1ddb4d7:471244e7
2025-05-24 11:00:37
@ b1ddb4d7:471244e7
2025-05-24 11:00:37Bitcoin FilmFest (BFF25) returns to Warsaw for its third edition, blending independent cinema—from feature films and commercials to AI-driven experimental visuals—with education and entertainment.
Hundreds of attendees from around the world will gather for three days of screenings, discussions, workshops, and networking at the iconic Kinoteka Cinema (PKiN), the same venue that hosted the festival’s first two editions in March 2023 and April 2024.
This year’s festival, themed “Beyond the Frame,” introduces new dimensions to its program, including an extra day on May 22 to celebrate Bitcoin Pizza Day, the first real-world bitcoin transaction, with what promises to be one of Europe’s largest commemorations of this milestone.
BFF25 bridges independent film, culture, and technology, with a bold focus on decentralized storytelling and creative expression. As a community-driven cultural experience with a slightly rebellious spirit, Bitcoin FilmFest goes beyond movies, yet cinema remains at its heart.
Here’s a sneak peek at the lineup, specially curated for movie buffs:
 Generative Cinema – A special slot with exclusive shorts and a thematic debate on the intersection of AI and filmmaking. Featured titles include, for example: BREAK FREE, SATOSHI: THE CREATION OF BITCOIN, STRANGE CURRENCIES, and BITCOIN IS THE MYCELIUM OF MONEY, exploring financial independence, traps of the fiat system, and a better future built on sound money.
Generative Cinema – A special slot with exclusive shorts and a thematic debate on the intersection of AI and filmmaking. Featured titles include, for example: BREAK FREE, SATOSHI: THE CREATION OF BITCOIN, STRANGE CURRENCIES, and BITCOIN IS THE MYCELIUM OF MONEY, exploring financial independence, traps of the fiat system, and a better future built on sound money. Upcoming Productions Preview – A bit over an hour-long block of unreleased pilots and works-in-progress. Attendees will get exclusive first looks at projects like FINDING HOME (a travel-meets-personal-journey series), PARALLEL SPACES (a story about alternative communities), and THE LEGEND OF LANDI (a mysterious narrative).
Upcoming Productions Preview – A bit over an hour-long block of unreleased pilots and works-in-progress. Attendees will get exclusive first looks at projects like FINDING HOME (a travel-meets-personal-journey series), PARALLEL SPACES (a story about alternative communities), and THE LEGEND OF LANDI (a mysterious narrative). Freedom-Focused Ads & Campaigns – Unique screenings of video commercials, animations, and visual projects, culminating in “The PoWies” (Proof of Work-ies)—the first ever awards show honoring the best Bitcoin-only awareness campaigns.
Freedom-Focused Ads & Campaigns – Unique screenings of video commercials, animations, and visual projects, culminating in “The PoWies” (Proof of Work-ies)—the first ever awards show honoring the best Bitcoin-only awareness campaigns.To get an idea of what might come up at the event, here, you can preview 6 selected ads combined into two 2 videos:
 Open Pitch Competition – A chance for filmmakers to present fresh ideas and unfinished projects to an audience of a dedicated jury, movie fans and potential collaborators. This competitive block isn’t just entertaining—it’s a real opportunity for creators to secure funding and partnerships.
Open Pitch Competition – A chance for filmmakers to present fresh ideas and unfinished projects to an audience of a dedicated jury, movie fans and potential collaborators. This competitive block isn’t just entertaining—it’s a real opportunity for creators to secure funding and partnerships. Golden Rabbit Awards: A lively gala honoring films from the festival’s Official Selection, with awards in categories like Best Feature, Best Story, Best Short, and Audience Choice.
Golden Rabbit Awards: A lively gala honoring films from the festival’s Official Selection, with awards in categories like Best Feature, Best Story, Best Short, and Audience Choice.BFF25 Main Screenings
Sample titles from BFF25’s Official Selection:
 REVOLUCIÓN BITCOIN – A documentary by Juan Pablo, making its first screening outside the Spanish-speaking world in Warsaw this May. Three years of important work, 80 powerful minutes to experience. The film explores Bitcoin’s impact across Argentina, Colombia, Mexico, El Salvador, and Spain through around 40 diverse perspectives. Screening in Spanish with English subtitles, followed by a Q&A with the director.
REVOLUCIÓN BITCOIN – A documentary by Juan Pablo, making its first screening outside the Spanish-speaking world in Warsaw this May. Three years of important work, 80 powerful minutes to experience. The film explores Bitcoin’s impact across Argentina, Colombia, Mexico, El Salvador, and Spain through around 40 diverse perspectives. Screening in Spanish with English subtitles, followed by a Q&A with the director. UNBANKABLE – Luke Willms’ directorial debut, drawing from his multicultural roots and his father’s pioneering HIV/AIDS research. An investigative documentary based on Luke’s journeys through seven African countries, diving into financial experiments and innovations—from mobile money and digital lending to Bitcoin—raising smart questions and offering potential lessons for the West. Its May appearance at BFF25 marks its largest European event to date, following festival screenings and nominations across multiple continents over the past year.
UNBANKABLE – Luke Willms’ directorial debut, drawing from his multicultural roots and his father’s pioneering HIV/AIDS research. An investigative documentary based on Luke’s journeys through seven African countries, diving into financial experiments and innovations—from mobile money and digital lending to Bitcoin—raising smart questions and offering potential lessons for the West. Its May appearance at BFF25 marks its largest European event to date, following festival screenings and nominations across multiple continents over the past year. HOTEL BITCOIN – A Spanish comedy directed by Manuel Sanabria and Carlos “Pocho” Villaverde. Four friends, 4,000 bitcoins , and one laptop spark a chaotic adventure of parties, love, crime, and a dash of madness. Exploring sound money, value, and relationships through a twisting plot. The film premiered at the Tarazona and Moncayo Comedy Film Festival in August 2024. Its Warsaw screening at BFF25 (in Spanish with English subtitles) marks its first public showing outside the Spanish-speaking world.
HOTEL BITCOIN – A Spanish comedy directed by Manuel Sanabria and Carlos “Pocho” Villaverde. Four friends, 4,000 bitcoins , and one laptop spark a chaotic adventure of parties, love, crime, and a dash of madness. Exploring sound money, value, and relationships through a twisting plot. The film premiered at the Tarazona and Moncayo Comedy Film Festival in August 2024. Its Warsaw screening at BFF25 (in Spanish with English subtitles) marks its first public showing outside the Spanish-speaking world.Check out trailers for this year’s BFF25 and past editions on YouTube.
Tickets & Info:
- Detailed program and tickets are available at bitcoinfilmfest.com/bff25.
- Stay updated via the festival’s official channels (links provided on the website).
- Use ‘LN-NEWS’ to get 10% of tickets
-
 @ b1ddb4d7:471244e7
2025-05-24 11:00:35
@ b1ddb4d7:471244e7
2025-05-24 11:00:35Starting January 1, 2026, the United Kingdom will impose some of the world’s most stringent reporting requirements on cryptocurrency firms.
All platforms operating in or serving UK customers-domestic and foreign alike-must collect and disclose extensive personal and transactional data for every user, including individuals, companies, trusts, and charities.
This regulatory drive marks the UK’s formal adoption of the OECD’s Crypto-Asset Reporting Framework (CARF), a global initiative designed to bring crypto oversight in line with traditional banking and to curb tax evasion in the rapidly expanding digital asset sector.
What Will Be Reported?
Crypto firms must gather and submit the following for each transaction:
- User’s full legal name, home address, and taxpayer identification number
- Detailed data on every trade or transfer: type of cryptocurrency, amount, and nature of the transaction
- Identifying information for corporate, trust, and charitable clients
The obligation extends to all digital asset activities, including crypto-to-crypto and crypto-to-fiat trades, and applies to both UK residents and non-residents using UK-based platforms. The first annual reports covering 2026 activity are due by May 31, 2027.
Enforcement and Penalties
Non-compliance will carry stiff financial penalties, with fines of up to £300 per user account for inaccurate or missing data-a potentially enormous liability for large exchanges. The UK government has urged crypto firms to begin collecting this information immediately to ensure operational readiness.
Regulatory Context and Market Impact
This move is part of a broader UK strategy to position itself as a global fintech hub while clamping down on fraud and illicit finance. UK Chancellor Rachel Reeves has championed these measures, stating, “Britain is open for business – but closed to fraud, abuse, and instability”. The regulatory expansion comes amid a surge in crypto adoption: the UK’s Financial Conduct Authority reported that 12% of UK adults owned crypto in 2024, up from just 4% in 2021.
Enormous Risks for Consumers: Lessons from the Coinbase Data Breach
While the new framework aims to enhance transparency and protect consumers, it also dramatically increases the volume of sensitive personal data held by crypto firms-raising the stakes for cybersecurity.
The risks are underscored by the recent high-profile breach at Coinbase, one of the world’s largest exchanges.
In May 2025, Coinbase disclosed that cybercriminals, aided by bribed offshore contractors, accessed and exfiltrated customer data including names, addresses, government IDs, and partial bank details.
The attackers then used this information for sophisticated phishing campaigns, successfully deceiving some customers into surrendering account credentials and funds.
“While private encryption keys remained secure, sufficient customer information was exposed to enable sophisticated phishing attacks by criminals posing as Coinbase personnel.”
Coinbase now faces up to $400 million in compensation costs and has pledged to reimburse affected users, but the incident highlights the systemic vulnerability created when large troves of personal data are centralized-even if passwords and private keys are not directly compromised. The breach also triggered a notable drop in Coinbase’s share price and prompted a $20 million bounty for information leading to the attackers’ capture.
The Bottom Line
The UK’s forthcoming crypto reporting regime represents a landmark in financial regulation, promising greater transparency and tax compliance. However, as the Coinbase episode demonstrates, the aggregation of sensitive user data at scale poses a significant cybersecurity risk.
As regulators push for more oversight, the challenge will be ensuring that consumer protection does not become a double-edged sword-exposing users to new threats even as it seeks to shield them from old ones.
-
 @ b1ddb4d7:471244e7
2025-05-24 11:00:34
@ b1ddb4d7:471244e7
2025-05-24 11:00:34This article was originally published on aier.org
Even after eleven years experience, and a per Bitcoin price of nearly $20,000, the incredulous are still with us. I understand why. Bitcoin is not like other traditional financial assets.
Even describing it as an asset is misleading. It is not the same as a stock, as a payment system, or a money. It has features of all these but it is not identical to them.
What Bitcoin is depends on its use as a means of storing and porting value, which in turn rests of secure titles to ownership of a scarce good. Those without experience in the sector look at all of this and get frustrated that understanding why it is valuable is not so easy to grasp.
In this article, I’m updating an analysis I wrote six years ago. It still holds up. For those who don’t want to slog through the entire article, my thesis is that Bitcoin’s value obtains from its underlying technology, which is an open-source ledger that keeps track of ownership rights and permits the transfer of these rights. Bitcoin managed to bundle its unit of account with a payment system that lives on the ledger. That’s its innovation and why it obtained a value and that value continues to rise.
Consider the criticism offered by traditional gold advocates, who have, for decades, pushed the idea that sound money must be backed by something real, hard, and independently valuable. Bitcoin doesn’t qualify, right? Maybe it does.
Bitcoin first emerged as a possible competitor to national, government-managed money in 2009. Satoshi Nakamoto’s white paper was released October 31, 2008. The structure and language of this paper sent the message: This currency is for computer technicians, not economists nor political pundits. The paper’s circulation was limited; novices who read it were mystified.
But the lack of interest didn’t stop history from moving forward. Two months later, those who were paying attention saw the emergence of the “Genesis Block,” the first group of bitcoins generated through Nakamoto’s concept of a distributed ledger that lived on any computer node in the world that wanted to host it.
Here we are all these years later and a single bitcoin trades at $18,500. The currency is held and accepted by many thousands of institutions, both online and offline. Its payment system is very popular in poor countries without vast banking infrastructures but also in developed countries. And major institutions—including the Federal Reserve, the OECD, the World Bank, and major investment houses—are paying respectful attention and weaving blockchain technology into their operations.
Enthusiasts, who are found in every country, say that its exchange value will soar even more in the future because its supply is strictly limited and it provides a system vastly superior to government money. Bitcoin is transferred between individuals without a third party. It is relatively low-cost to exchange. It has a predictable supply. It is durable, fungible, and divisible: all crucial features of money. It creates a monetary system that doesn’t depend on trust and identity, much less on central banks and government. It is a new system for the digital age.
Hard lessons for hard money
To those educated in the “hard money” tradition, the whole idea has been a serious challenge. Speaking for myself, I had been reading about bitcoin for two years before I came anywhere close to understanding it. There was just something about the whole idea that bugged me. You can’t make money out of nothing, much less out of computer code. Why does it have value then? There must be something amiss. This is not how we expected money to be reformed.
There’s the problem: our expectations. We should have been paying closer attention to Ludwig von Mises’ theory of money’s origins—not to what we think he wrote, but to what he actually did write.
In 1912, Mises released The Theory of Money and Credit. It was a huge hit in Europe when it came out in German, and it was translated into English. While covering every aspect of money, his core contribution was in tracing the value and price of money—and not just money itself—to its origins. That is, he explained how money gets its price in terms of the goods and services it obtains. He later called this process the “regression theorem,” and as it turns out, bitcoin satisfies the conditions of the theorem.
Mises’ teacher, Carl Menger, demonstrated that money itself originates from the market—not from the State and not from social contract. It emerges gradually as monetary entrepreneurs seek out an ideal form of commodity for indirect exchange. Instead of merely bartering with each other, people acquire a good not to consume, but to trade. That good becomes money, the most marketable commodity.
But Mises added that the value of money traces backward in time to its value as a bartered commodity. Mises said that this is the only way money can have value.
The theory of the value of money as such can trace back the objective exchange value of money only to that point where it ceases to be the value of money and becomes merely the value of a commodity…. If in this way we continually go farther and farther back we must eventually arrive at a point where we no longer find any component in the objective exchange value of money that arises from valuations based on the function of money as a common medium of exchange; where the value of money is nothing other than the value of an object that is useful in some other way than as money…. Before it was usual to acquire goods in the market, not for personal consumption, but simply in order to exchange them again for the goods that were really wanted, each individual commodity was only accredited with that value given by the subjective valuations based on its direct utility.
Mises’ explanation solved a major problem that had long mystified economists. It is a narrative of conjectural history, and yet it makes perfect sense. Would salt have become money had it otherwise been completely useless? Would beaver pelts have obtained monetary value had they not been useful for clothing? Would silver or gold have had money value if they had no value as commodities first? The answer in all cases of monetary history is clearly no. The initial value of money, before it becomes widely traded as money, originates in its direct utility. It’s an explanation that is demonstrated through historical reconstruction. That’s Mises’ regression theorem.
Bitcoin’s Use Value
At first glance, bitcoin would seem to be an exception. You can’t use a bitcoin for anything other than money. It can’t be worn as jewelry. You can’t make a machine out of it. You can’t eat it or even decorate with it. Its value is only realized as a unit that facilitates indirect exchange. And yet, bitcoin already is money. It’s used every day. You can see the exchanges in real time. It’s not a myth. It’s the real deal.
It might seem like we have to choose. Is Mises wrong? Maybe we have to toss out his whole theory. Or maybe his point was purely historical and doesn’t apply in the future of a digital age. Or maybe his regression theorem is proof that bitcoin is just an empty mania with no staying power, because it can’t be reduced to its value as a useful commodity.
And yet, you don’t have to resort to complicated monetary theory in order to understand the sense of alarm surrounding bitcoin. Many people, as I did, just have a feeling of uneasiness about a money that has no basis in anything physical. Sure, you can print out a bitcoin on a piece of paper, but having a paper with a QR code or a public key is not enough to relieve that sense of unease.
How can we resolve this problem? In my own mind, I toyed with the issue for more than a year. It puzzled me. I wondered if Mises’ insight applied only in a pre-digital age. I followed the speculations online that the value of bitcoin would be zero but for the national currencies into which it is converted. Perhaps the demand for bitcoin overcame the demands of Mises’ scenario because of a desperate need for something other than the dollar.
As time passed—and I read the work of Konrad Graf, Peter Surda, and Daniel Krawisz—finally the resolution came. Bitcoin is both a payment system and a money. The payment system is the source of value, while the accounting unit merely expresses that value in terms of price. The unity of money and payment is its most unusual feature, and the one that most commentators have had trouble wrapping their heads around.
We are all used to thinking of currency as separate from payment systems. This thinking is a reflection of the technological limitations of history. There is the dollar and there are credit cards. There is the euro and there is PayPal. There is the yen and there are wire services. In each case, money transfer relies on third-party service providers. In order to use them, you need to establish what is called a “trust relationship” with them, which is to say that the institution arranging the deal has to believe that you are going to pay.
This wedge between money and payment has always been with us, except for the case of physical proximity.
If I give you a dollar for your pizza slice, there is no third party. But payment systems, third parties, and trust relationships become necessary once you leave geographic proximity. That’s when companies like Visa and institutions like banks become indispensable. They are the application that makes the monetary software do what you want it to do.
The hitch is that
-
 @ b1ddb4d7:471244e7
2025-05-24 11:00:32
@ b1ddb4d7:471244e7
2025-05-24 11:00:32Breez, a leader in Lightning Network infrastructure, and Spark, a bitcoin-native Layer 2 (L2) platform, today announced a groundbreaking collaboration to empower developers with tools to seamlessly integrate self-custodial bitcoin payments into everyday applications.
The partnership introduces a new implementation of the Breez SDK built on Spark’s bitcoin-native infrastructure, accelerating the evolution of bitcoin from “digital gold” to a global, permissionless currency.
The Breez SDK is expanding

We’re joining forces with @buildonspark to release a new nodeless implementation of the Breez SDK — giving developers the tools they need to bring Bitcoin payments to everyday apps.
Bitcoin-Native
Powered by Spark’s…— Breez
 (@Breez_Tech) May 22, 2025
(@Breez_Tech) May 22, 2025A Bitcoin-Native Leap for Developers
The updated Breez SDK leverages Spark’s L2 architecture to deliver a frictionless, bitcoin-native experience for developers.
Key features include:
- Universal Compatibility: Bindings for all major programming languages and frameworks.
- LNURL & Lightning Address Support: Streamlined integration for peer-to-peer transactions.
- Real-Time Interaction: Instant mobile notifications for payment confirmations.
- No External Reliance: Built directly on bitcoin via Spark, eliminating bridges or third-party consensus.
This implementation unlocks use cases such as streaming content payments, social app monetization, in-game currencies, cross-border remittances, and AI micro-settlements—all powered by Bitcoin’s decentralized network.
Quotes from Leadership
Roy Sheinfeld, CEO of Breez:
“Developers are critical to bringing bitcoin into daily life. By building the Breez SDK on Spark’s revolutionary architecture, we’re giving builders a bitcoin-native toolkit to strengthen Lightning as the universal language of bitcoin payments.”Kevin Hurley, Creator of Spark:
“This collaboration sets the standard for global peer-to-peer transactions. Fast, open, and embedded in everyday apps—this is bitcoin’s future. Together, we’re equipping developers to create next-generation payment experiences.”David Marcus, Co-Founder and CEO of Lightspark:
“We’re thrilled to see developers harness Spark’s potential. This partnership marks an exciting milestone for the ecosystem.”Collaboration Details
As part of the agreement, Breez will operate as a Spark Service Provider (SSP), joining Lightspark in facilitating payments and expanding Spark’s ecosystem. Technical specifications for the SDK will be released later this year, with the full implementation slated for launch in 2025.About Breez
Breez pioneers Lightning Network solutions, enabling developers to embed self-custodial bitcoin payments into apps. Its SDK powers seamless, secure, and decentralized financial interactions.About Spark
Spark is a bitcoin-native Layer 2 infrastructure designed for payments and settlement, allowing developers to build directly on Bitcoin’s base layer without compromises. -
 @ 1d7ff02a:d042b5be
2025-05-24 10:15:40
@ 1d7ff02a:d042b5be
2025-05-24 10:15:40ຄົນສ່ວນຫຼາຍມັກຈະມອງເຫັນ Bitcoin ເປັນສິນຊັບທີ່ມີຄວາມສ່ຽງສູງ ເນື່ອງຈາກມີອັດຕາການປ່ຽນແປງລາຄາທີ່ຮຸນແຮງແລະກວ້າງຂວາງໃນໄລຍະສັ້ນໆ. ແຕ່ຄວາມຈິງແລ້ວ ຄວາມຜັນຜວນຂອງ Bitcoin ແມ່ນຄຸນລັກສະນະພິເສດທີ່ສຳຄັນຂອງມັນ ບໍ່ແມ່ນຂໍ້ບົກພ່ອງ.
ລາຄາແມ່ນຫຍັງ?
ເພື່ອເຂົ້າໃຈເລື້ອງນີ້ດີຂຶ້ນ ເຮົາຕ້ອງເຂົ້າໃຈກ່ອນວ່າລາຄາໝາຍເຖິງຫຍັງ. ລາຄາແມ່ນການສະທ້ອນຄວາມຄິດເຫັນແລະການປະເມີນມູນຄ່າຂອງຜູ້ຊື້ແລະຜູ້ຂາຍໃນເວລາໃດໜຶ່ງ. ການຕັດສິນໃຈຊື້ຫຼືຂາຍໃນລາຄາໃດໜຶ່ງ ກໍແມ່ນການສື່ສານກັບຕະຫຼາດ ແລະກົນໄກຂອງຕະຫຼາດຈະຄ້ົນຫາແລະກໍານົດລາຄາທີ່ແທ້ຈິງຂອງສິນຊັບນັ້ນ.
ເປັນຫຍັງ Bitcoin ຈຶ່ງຜັນຜວນ?
Bitcoin ຖືກສ້າງຂຶ້ນບົນພື້ນຖານອິນເຕີເນັດ ເຮັດໃຫ້ການສື່ສານຄວາມຄິດເຫັນຂອງຜູ້ຄົນສາມາດເຮັດໄດ້ຢ່າງໄວວາ. ຍິ່ງໄປກວ່ານັ້ນ Bitcoin ມີລັກສະນະກະຈາຍສູນ (decentralized) ແລະບໍ່ມີຜູ້ຄວບຄຸມສູນກາງ ຈຶ່ງເຮັດໃຫ້ຄົນສາມາດຕັດສິນໃຈຊື້ຂາຍໄດ້ຢ່າງໄວວາ.
ສິ່ງນີ້ເຮັດໃຫ້ລາຄາຂອງ Bitcoin ສາມາດສະທ້ອນຄວາມຄິດເຫັນຂອງຄົນໄດ້ແບບເວລາຈິງ (real-time). ແລະເນື່ອງຈາກມະນຸດເຮົາມີຄວາມຄິດທີ່ບໍ່ແນ່ນອນ ມີການປ່ຽນແປງ ລາຄາຂອງ Bitcoin ຈຶ່ງປ່ຽນແປງໄປຕາມຄວາມຄິດເຫັນລວມຂອງຜູ້ຄົນແບບທັນທີ.
ປັດໄຈທີ່ເພີ່ມຄວາມຜັນຜວນ:
ຂະໜາດຕະຫຼາດທີ່ຍັງນ້ອຍ: ເມື່ອປຽບທຽບກັບຕະຫຼາດການເງິນແບບດັ້ງເດີມ ຕະຫຼາດ Bitcoin ຍັງມີຂະໜາດນ້ອຍ ເຮັດໃຫ້ການຊື້ຂາຍຈຳນວນໃຫຍ່ສາມາດສົ່ງຜົນກະທົບຕໍ່ລາຄາໄດ້ຫຼາຍ.
ການຄ້າຂາຍຕະຫຼອດ 24/7: ບໍ່ເຫມືອນກັບຕະຫຼາດຫຼັກຊັບທີ່ມີເວລາເປີດປິດ Bitcoin ສາມາດຊື້ຂາຍໄດ້ຕະຫຼອດເວລາ ເຮັດໃຫ້ການປ່ຽນແປງລາຄາສາມາດເກີດຂຶ້ນໄດ້ທຸກເວລາ.
ການປຽບທຽບກັບສິນຊັບອື່ນ
ເມື່ອປຽບທຽບກັບສິນຊັບອື່ນທີ່ມີການຄວບຄຸມ ເຊັ່ນ ສະກຸນເງິນທ້ອງຖິ່ນຫຼືທອງຄຳ ທີ່ເບິ່ງຄືວ່າມີຄວາມຜັນຜວນໜ້ອຍກວ່າ Bitcoin ນັ້ນ ບໍ່ແມ່ນຫມາຍຄວາມວ່າພວກມັນບໍ່ມີຄວາມຜັນຜວນ. ແຕ່ເປັນເພາະມີການຄວບຄຸມຈາກອົງການສູນກາງ ເຮັດໃຫ້ການສື່ສານຄວາມຄິດເຫັນຂອງຄົນໄປຮອດຕະຫຼາດບໍ່ແບບເວລາຈິງ.
ດັ່ງນັ້ນ ສິ່ງທີ່ເຮົາເຫັນແມ່ນການຊັກຊ້າ (delay) ໃນການສະແດງຄວາມຄິດເຫັນທີ່ແທ້ຈິງອອກມາເທົ່ານັ້ນ ບໍ່ແມ່ນຄວາມໝັ້ນຄົງຂອງມູນຄ່າ.
ກົນໄກການຄວບຄຸມແລະຜົນກະທົບ:
ສະກຸນເງິນ: ທະນາຄານກາງສາມາດພິມເງິນ ປັບອັດຕາດອກເບີ້ຍ ແລະແຊກແຊງຕະຫຼາດ ເຮັດໃຫ້ລາຄາບໍ່ສະທ້ອນມູນຄ່າທີ່ແທ້ຈິງໃນທັນທີ.
ຫຼັກຊັບ: ມີລະບຽບການຫຼາຍຢ່າງ ເຊັ່ນ ການຢຸດການຊື້ຂາຍເມື່ອລາຄາປ່ຽນແປງຫຼາຍເກີນໄປ (circuit breakers) ທີ່ຂັດຂວາງການສະແດງຄວາມຄິດເຫັນທີ່ແທ້ຈິງ.
ທອງຄຳ: ຖຶງແມ່ນຈະເປັນສິນຊັບທີ່ບໍ່ມີການຄວບຄຸມ ແຕ່ຕະຫຼາດທອງຄຳມີຂະໜາດໃຫຍ່ກວ່າ Bitcoin ຫຼາຍ ແລະມີການຄ້າແບບດັ້ງເດີມທີ່ຊ້າກວ່າ.
ບົດສະຫຼຸບ
ການປຽບທຽບຄວາມຜັນຜວນລະຫວ່າງ Bitcoin ແລະສິນຊັບອື່ນໆ ໂດຍໃຊ້ໄລຍະເວລາສັ້ນນັ້ນ ບໍ່ມີຄວາມສົມເຫດສົມຜົນປານໃດ ເພາະວ່າປັດໄຈເລື້ອງການຊັກຊ້າໃນການສະແດງຄວາມຄິດເຫັນນີ້ແມ່ນສິ່ງສຳຄັນທີ່ສົ່ງຜົນຕໍ່ລາຄາທີ່ແທ້ຈິງ.
ສິ່ງທີ່ຄວນເຮັດແທ້ໆແມ່ນການນຳເອົາກອບເວລາທີ່ກວ້າງຂວາງກວ່າມາວິເຄາະ ເຊັ່ນ ເປັນປີຫຼືຫຼາຍປີ ແລ້ວຈຶ່ງປຽບທຽບ. ດ້ວຍວິທີນີ້ ເຮົາຈຶ່ງຈະເຫັນປະສິດທິຜົນແລະການດຳເນີນງານທີ່ແທ້ຈິງຂອງ Bitcoin ໄດ້ຢ່າງຈະແຈ້ງ
-
 @ 0b118e40:4edc09cb
2025-05-15 15:40:21
@ 0b118e40:4edc09cb
2025-05-15 15:40:21My week started off with a lovely message from a friend : “I often think about you. Especially during times when it requires me to be more resilient and have faith in myself. I always carry your note in the book you gave me, “what the dog saw” And it always gives me courage and I send a little prayer your way”.
This friend of mine was dealing with the undercurrent of discrimination in my alma mater when we first met, and I helped out. It's something anybody would have done, but surprisingly, nobody else showed up. We’ve stayed in touch over the years, and my friend went on to help a lot of other people along the way.
I don’t remember what I wrote in that note. It’s something I tend to do (write notes, give books, write notes in books). But the message boomeranged back to me at a time when I needed to hold the line. To keep the faith.
Most of us don’t talk about our struggles. And sometimes the smallest act, which could just be a kind word or a reminder of the person you are, can carry farther than we imagine.
On the act of giving
There’s a book called Give and Take by Adam Grant. I picked it up hoping to learn how to take, because it’s always been easier to give and harder to accept help. But what I learned was something else entirely.
Grant studied over 30,000 people across different companies and grouped them into three types: * Givers * Matchers * Takers
Based on his studies, givers often finish last... They struggle the most. They burn out. They get overlooked. They’re too trusting.
But oddly, they also rise to the very top.
Matchers are the scorekeepers, the “I’ll help you if you help me” kind. They make up most of the population. The fascinating thing about tit-for-tat is that if someone’s kind, they reciprocate. But if someone acts like a jerk, they return the energy, and over time, it becomes a pool of spoiled milk. Matchers are a lukewarm, forgettable kind of network.
Takers are the ones chasing attention, always aligning themselves with whoever looks powerful. They tend to float toward status and soak up what they can. But they often portray themselves as kind and giving.
One example Grant shared was Enron's Kenneth Lay, who was at the center of one of the biggest corporate scandals in U.S. history. He hung around wherever he’d get seen or validated. He funded both Bush and Clinton, hedging his bets on who might win by securing proximity. Sadly, when Enron crumbled, he died of a heart attack before his prison sentencing.
Most people steer clear from takers because they are just exhausting. And takers often collapse under the weight of their own games.
But takers aren’t the lowest performers. That spot belongs to a certain kind of giver—the self-neglecting kind. The ones with no boundaries, no clarity, and no self-awareness. They give in to avoid conflict, to feel worthy, or because they don’t know how to say no. And when life breaks them, they point fingers.
Then there’s the other kind of giver. The ones who build trust and build people up without asking for a receipt.
These givers: 1. Give without expectation, from a place of purpose 2. Build and uplift others without seeking credit 3. Set boundaries and walk away when giving turns into draining
This group of givers rarely talk much about what they do for others. But when you hear about it or see it, it stays with you. It makes you want to show up a little better.
Why open source environments feels like home
The more I thought about it, the more I saw how deeply open source reflects that kind of giving that ends up right at the top.
In open source, you don’t last if it’s just about ego. You can’t fake it. There are no titles, no awards. You either show up to build and help, or you don’t.
People who give without needing to be seen are the ones the community leans on. You can tell when someone’s pretending to care. It’s in their tone, their urgency and their sense of transaction. The genuine ones don’t need to brand themselves as generous. They just are.
Open source works because giving is the default setting. The work speaks volumes and generosity compounds. The system filters for people who show up with purpose and stay consistent.
It’s also why the ones who whine, posture, or manipulate rarely last. They might call themselves givers, but they’re not fooling anyone who’s actually doing the work.
Adam Grant found that for giver cultures to thrive, takers have to be removed. They need to be pruned. Because takers poison the well. They drain givers, shift the culture from contribution to calculation, and unravel the trust that holds open systems together.
When hope boomerangs
That note is something I don’t remember writing. But it found its way back to me, and it was a good reminder to take my own advice and keep the faith.
And maybe that’s the point.
You do a small thing. And years later, it circles back when it matters most. Not because you expected it. But because you mattered.
According to Grant, givers do best when they combine generosity with grit and strategy. They create networks built on goodwill, which eventually open doors others don’t even know exist.
So if you’re wondering where I’m going with this, do something genuinely kind for someone today. Even if it’s as simple as sending a kind note. Not for you to be seen or heard. And not for you to keep scores.
But, just because.
-
 @ b1ddb4d7:471244e7
2025-05-24 10:00:42
@ b1ddb4d7:471244e7
2025-05-24 10:00:42Asia has emerged as a powerhouse for bitcoin adoption, with diverse countries across the region embracing the world’s leading digital currency in unique ways.
From institutional investors in Singapore to grassroots movements in Indonesia, the Asian bitcoin ecosystem presents a fascinating tapestry of innovation, regulation, and community-driven initiatives.
We dive deep into the current state of bitcoin adoption across key Asian markets, providing investors with actionable insights into this dynamic region.
The Numbers: Asia’s Bitcoin Dominance
As of early 2025, over 500 million people worldwide hold some form of digital currency, with bitcoin remaining the most widely adopted digital asset. Asia stands at the forefront of this adoption wave, with the Central & Southern Asia and Oceania (CSAO) region leading the world in digital currency adoption according to Chainalysis’s 2024 Global Crypto Adoption Index.
The statistics paint a compelling picture:
- Seven of the top 20 countries in global crypto adoption are located in the CSAO region.
- India and China together comprise almost half of the world’s digital currency user base.
- Japan’s digital currency market is expected to reach 19.43 million users by the end of 2025, with a penetration rate of 15.93%.
Behind these impressive numbers lies a complex ecosystem shaped by diverse factors including regulatory environments, technological infrastructure, economic necessities, and vibrant community initiatives.
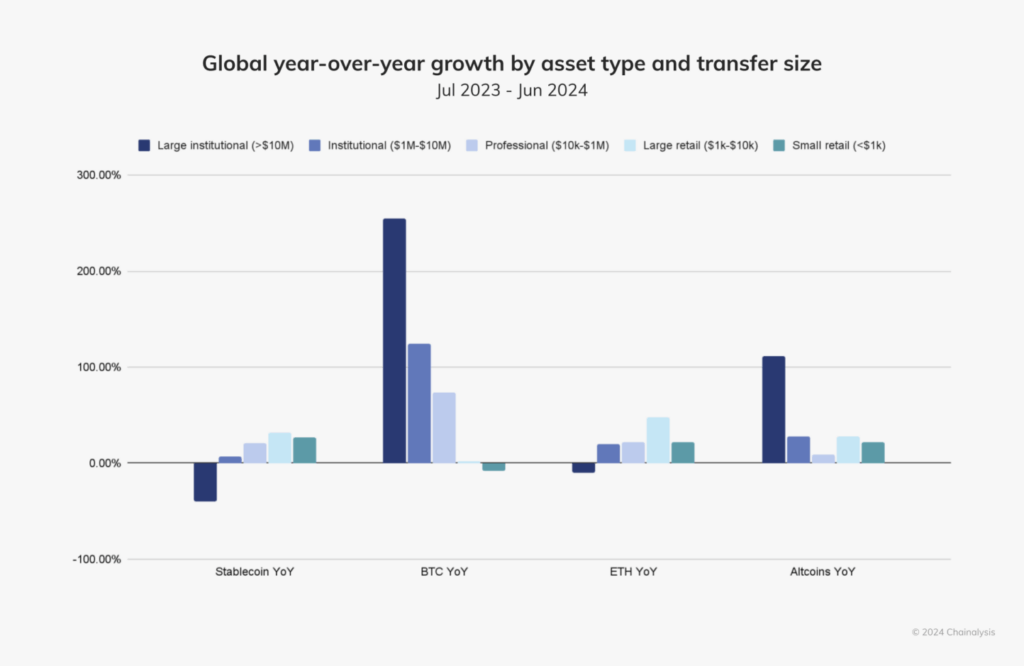
Photo Source: Chainalysis
Country-by-Country Analysis
India: The Grassroots Powerhouse
India ranks first in Chainalysis’s Global Crypto Adoption Index, with bitcoin adoption thriving particularly in tier-2 and tier-3 cities. This grassroots movement is driven primarily by:
- Financial inclusion: Bitcoin offers banking-like services to India’s large unbanked population.
- Remittance solutions: Lower fees for the significant Indian diaspora sending money home.
- Mobile wallet proliferation: India’s high smartphone penetration enables easy access to bitcoin services.
Japan: The Regulatory Pioneer
Japan has long played a significant role in bitcoin’s evolution, from hosting some of the earliest exchanges to pioneering regulatory clarity. In 2025, Japan finds itself at a fascinating crossroads:
- The Japan Financial Services Agency is considering reclassifying digital currency assets as financial products akin to stocks, potentially enhancing user protection.
- Major corporations like Metaplanet Inc. are expanding their bitcoin holdings, with plans to increase holdings by 470% to reach 10,000 BTC in 2025.
- The country boasts a thriving grassroots bitcoin community and a strong developer ecosystem.
Bitcoin adoption in Japan is uniquely balanced between institutional involvement and community enthusiasm, with initiatives like Blockstream’s Tokyo office working to promote layer-2 solutions, self-custody, and developer education.
Vietnam: The P2P Leader
Vietnam consistently ranks among the top countries for bitcoin adoption per capita. The country’s relationship with bitcoin is characterized by:
- Strong peer-to-peer (P2P) platform usage for daily transactions and remittances.
- High mobile wallet adoption driving grassroots usage.
- Bitcoin serving as a hedge against local currency fluctuations.
- Relatively favorable regulatory attitude compared to some neighboring countries.
Singapore: The Institutional Hub
Singapore has established itself as Asia’s premier institutional bitcoin destination through:
- Clear and forward-thinking regulatory frameworks, particularly the Payment Services Act.
- Growing presence of global digital currency firms including Gemini, OKX, and HashKey, which have received regulatory approvals.
- A robust financial infrastructure catering to high-net-worth individuals and institutional investors.
While Singapore’s consumer protection-focused framework restricts promotional activities and public advertising by digital currency service providers, the city-state remains a beacon for institutional bitcoin adoption in Asia.
South Korea: Retail Dominance Transitioning to Institutional
South Korea presents a fascinating case study of a market in transition:
- Retail investors currently dominate digital currency trading volume, while institutional participation significantly lags behind.
- Experts expect institutional involvement to increase, though a significant shift may not occur until around 2027.
- The local finance watchdog recently launched a crypto committee to assess permissions for corporate digital currency investors and ETFs.
- Users must access fiat-to-digital currency services through local exchanges with official banking partnerships, linking digital currency activities to legal identities.
Bitcoin Communities: The Grassroots Movements
What truly sets Asia apart in the global bitcoin landscape is the vibrant tapestry of community-driven initiatives across the region. These grassroots movements are instrumental in driving adoption from the ground up.
Bitcoin House Bali: A Community Hub
In Indonesia, the Bitcoin House Bali project exemplifies grassroots innovation. This initiative has transformed an old mining container into a vibrant hub for bitcoin education and community engagement.
Key features include:
- Free workshops (including “Bitcoin for Beginners” and “Bitcoin for Kids”).
- Developer programs including online classes, BitDevs Workshops, and Hackathons.
- A closed-loop economic system that turns bitcoin into community points.
- Merchant onboarding—from restaurants and drivers to scooter rentals and street vendors.
Bitcoin Seoul 2025: Bringing the Community Together
The upcoming Bitcoin Seoul 2025 conference (June 4-6, 2025) represents Asia’s largest bitcoin-focused gathering, bringing together global leaders, executives, and community members.
The event will feature:
- The Bitcoin Policy Summit: Seoul Edition, providing insights into regulatory trends.
- The Bitcoin Finance Forum, addressing institutional investment and treasury management.
- A Global Bitcoin Community Assembly for bitcoin grassroots and community leaders.
- Live Lightning Network payments demonstrations at the on-site Lightning Market.
This event underscores South Korea’s emerging role in the global Bitcoin ecosystem and highlights the growing institutional interest in the region.
Regulatory Landscapes: A Mixed Picture
The regulatory environment for bitcoin across Asia presents a complex and evolving picture that significantly impacts adoption patterns.
Japan’s Regulatory Evolution
Japan is considering tightening regulations on digital asset transactions by reclassifying them as financial products similar to stocks. If implemented, these changes would:
- Require issuers to disclose more detailed information on their corporate status.
- Potentially enhance user protection.
- Come into effect after June 2025, following policy direction outlines by the administration.
Current regulations in Japan are relatively digital currency-friendly, with bitcoin recognized as a legal form of payment under the Payment Services Act since 2016.
Singapore’s Balanced Approach
Singapore maintains a regulatory framework that emphasizes market stability and consumer protection, including:
- Restrictions on promoting digital services in public areas.
- The Payment Services Act that regulates digital currency exchanges.
- A general approach that supports institutional adoption while carefully managing retail exposure.
This balanced approach has helped establish Singapore as a trusted hub for bitcoin businesses and institutional investors.
South Korea’s Transitional Framework
South Korea’s regulatory landscape is in flux, with several developments impacting the bitcoin ecosystem:
- Corporate access to digital currenc
-
 @ b1ddb4d7:471244e7
2025-05-24 10:00:40
@ b1ddb4d7:471244e7
2025-05-24 10:00:40Global fintech leader Revolut has announced a landmark partnership with Lightspark, a pioneer in blockchain infrastructure solutions, to integrate bitcoin’s Lightning Network into its platform.
This collaboration, now live for Revolut users in the UK and select European Economic Area (EEA) countries, marks a transformative leap toward frictionless, real-time transactions—eliminating delays and exorbitant fees traditionally associated with digital asset transfers.
 Major update: @RevolutApp is now partnering with @lightspark pic.twitter.com/OUblgrj6Xr
Major update: @RevolutApp is now partnering with @lightspark pic.twitter.com/OUblgrj6Xr— Lightspark (@lightspark) May 7, 2025
Breaking Barriers in Digital Currency Usability
By adopting Lightspark’s cutting-edge technology, Revolut empowers its 40+ million customers to execute bitcoin transactions instantly at a fraction of current costs.
This integration addresses longstanding pain points in digital currency adoption, positioning bitcoin as a practical tool for everyday payments. Users can now seamlessly send, receive, and store bitcoin with the same ease as traditional fiat currencies, backed by Revolut’s secure platform.
The partnership also advances Revolut’s integration into the open Money Grid, a decentralized network enabling universal interoperability between financial platforms.
This move aligns Revolut with forward-thinking fintechs adopting next-gen solutions like Lightning transactions and Universal Money Addresses (UMA), which simplify cross-border payments by replacing complex wallet codes with human-readable addresses (e.g., $john.smith).
Why This Matters
The collaboration challenges conventional payment rails, which often incur delays of days and high fees for cross-border transfers. By contrast, Lightning Network transactions settle in seconds for minimal cost, revolutionizing peer-to-peer payments, remittances, and merchant settlements. For Revolut users, this means:
- Instant transactions: Send bitcoin globally in under three seconds.
- Near-zero fees: Dramatically reduce costs compared to traditional crypto transfers.
- Enhanced utility: Use bitcoin for daily spending, not just as a speculative asset.
The Road Ahead
Revolut plans to expand Lightning Network access to additional markets in 2025, with ambitions to integrate UMA support for seamless fiat and digital currency interactions. Lightspark will continue optimizing its infrastructure to support Revolut’s scaling efforts, further bridging the gap between blockchain innovation and mainstream finance.
About Revolut
Revolut is a global financial app serving over 40 million customers worldwide. Offering services ranging from currency exchange and stock trading to digital assets and insurance, Revolut is committed to building a borderless financial ecosystem.
About Lightspark
Founded by former PayPal and Meta executives, Lightspark develops enterprise-grade solutions for the Lightning Network. Its technology stack empowers institutions to harness bitcoin’s speed and efficiency while maintaining regulatory compliance.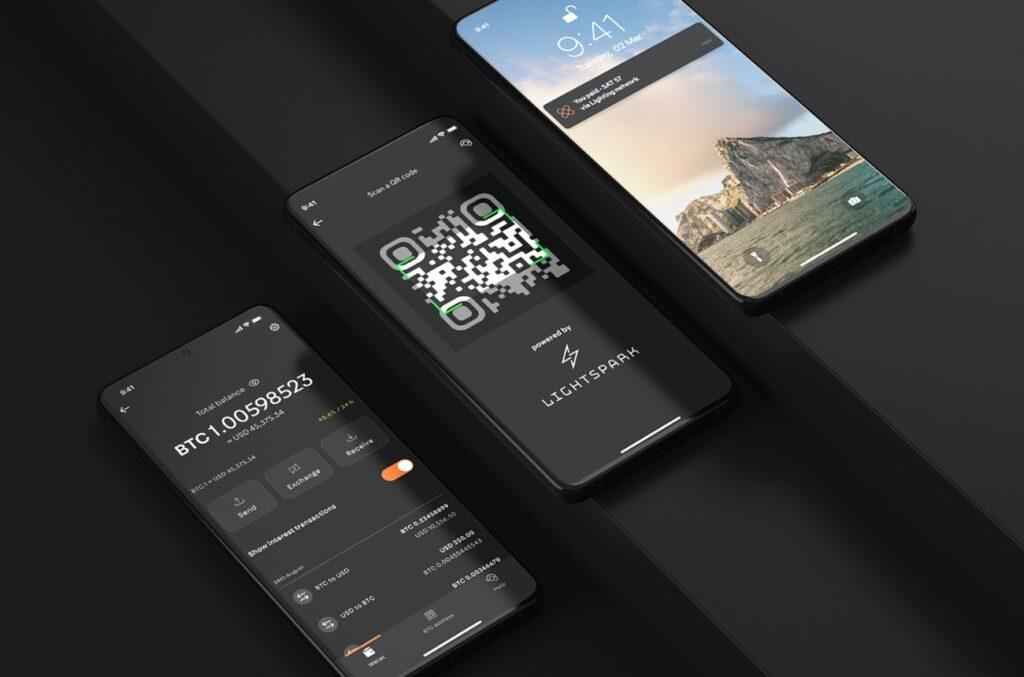
-
 @ b1ddb4d7:471244e7
2025-05-24 10:00:39
@ b1ddb4d7:471244e7
2025-05-24 10:00:39In the heart of East Africa, where M-Pesa reigns supreme and innovation pulses through bustling markets, a quiet revolution is brewing—one that could redefine how millions interact with money.
Enter Bitika, the Kenyan startup turning bitcoin’s complexity into a three-step dance, merging the lightning speed of sats with the trusted rhythm of mobile money.
At the helm is a founder whose “aha” moment came not in a boardroom, but at his kitchen table, watching his father grapple with the gap between understanding bitcoin and actually using it.
Bitika was born from that friction—a bridge between M-Pesa’s ubiquity and bitcoin’s borderless promise, wrapped in a name as playful as the Swahili slang that inspired it.
But this isn’t just a story about simplifying transactions. It’s about liquidity battles, regulatory tightropes, and a vision to turn Bitika into the invisible rails powering Africa’s Bitcoin future.
Building on Bitcoin
- Tell us a bit about yourself and how you got into bitcoin/fintech, and what keeps you passionate about this space?
I first came across bitcoin in 2020, but like many at that time, I didn’t fully grasp what it really was. It sounded too complicated, probably with the heavy terminologies. Over time, I kept digging deeper and became more curious.
I started digging into finance and how money works and realised this was what I needed to understand bitcoin’s objectives. I realized that bitcoin wasn’t just a new type of money—it was a breakthrough in how we think about freedom, ownership, and global finance.
What keeps me passionate is how bitcoin can empower people—especially in Africa—to take control of their wealth, without relying on unstable systems or middlemen.
- What pivotal moment or experience inspired you to create Bitika? Was there a specific gap in Kenya’s financial ecosystem that sparked the idea?
Yes, this idea was actually born right in my own home. I’ve always been an advocate for bitcoin, sharing it with friends, family, and even strangers. My dad and I had countless conversations about it. Eventually, he understood the concept. But when he asked, “How do I even buy bitcoin?” or “Can you just buy it for me?” and after taking him through binance—that hit me.
If someone I’d educated still found the buying process difficult, how many others were feeling the same way? That was the lightbulb moment. I saw a clear gap: the process of buying bitcoin was too technical for the average Kenyan. That’s the problem Bitika set out to solve.
- How did you identify the synergy between bitcoin and M-Pesa as a solution for accessibility?
M-Pesa is at the center of daily life in Kenya. Everyone uses it—from buying groceries to paying rent. Instead of forcing people to learn new tools, I decided to meet them where they already are. That synergy between M-Pesa and bitcoin felt natural. It’s about bridging what people already trust with something powerful and new.
- Share the story behind the name “Bitika” – does it hold a cultural or symbolic meaning?
Funny enough, Bitika isn’t a deeply planned name. It came while I was thinking about bitcoin and the type of transformation it brings to individuals. In Swahili, we often add “-ka” to words for flair—like “bambika” from “bamba.”
So, I just coined Bitika as a playful and catchy way to reflect something bitcoin-related, but also uniquely local. I stuck with it because thinking of an ideal brand name is the toughest challenge for me.
- Walk us through the user journey – how does buying bitcoin via M-Pesa in “3 simple steps” work under the hood?
It’s beautifully simple.
1. The user enters the amount they want to spend in KES—starting from as little as 50 KES (about $0.30).
2. They input their Lightning wallet address.
3. They enter their M-Pesa number, which triggers an STK push (payment prompt) on their phone. Once confirmed—pap!—they receive bitcoin almost instantly.
Under the hood, we fetch the live BTC price, validate wallet addresses, check available liquidity, process the mobile payment, and send sats via the Lightning Network—all streamlined into a smooth experience for the user.
- Who’s Bitika’s primary audience? Are you focusing on unbanked populations, tech enthusiasts, or both?
Both. Bitika is designed for everyday people—especially the unbanked and underbanked who are excluded from traditional finance. But we also attract bitcoiners who just want a faster, easier way to buy sats. What unites them is the desire for a seamless and low-barrier bitcoin experience.
Community and Overcoming Challenges
- What challenges has Bitika faced navigating Kenya’s bitcoin regulations, and how do you build trust with regulators?
Regulation is still evolving here. Parliament has drafted bills, but none have been passed into law yet. We’re currently in a revision phase where policymakers are trying to strike a balance between encouraging innovation and protecting the public.
We focus on transparency and open dialogue—we believe that building trust with regulators starts with showing how bitcoin can serve the public good.
- What was the toughest obstacle in building Bitika, and how did you overcome it?
Liquidity. Since we don’t have deep capital reserves, we often run into situations where we have to pause operations often to manually restock our bitcoin supply. It’s frustrating—for us and for users. We’re working on automating this process and securing funding to maintain consistent liquidity so users can access bitcoin at any time, without disruption.
This remains our most critical issue—and the primary reason we’re seeking support.
- Are you eyeing new African markets? What’s next for Bitika’s product?
Absolutely. The long-term vision is to expand Bitika into other African countries facing similar financial challenges. But first, we want to turn Bitika into a developer-first tool—infrastructure that others can build on. Imagine local apps, savings products, or financial tools built using Bitika’s simple bitcoin rails. That’s where we’re heading.
- What would you tell other African entrepreneurs aiming to disrupt traditional finance?
Disrupting finance sounds exciting—but the reality is messy. People fear what they don’t understand. That’s why simplicity is everything. Build tools that hide the complexity, and focus on making the user’s life easier. Most importantly, stay rooted in local context—solve problems people actually face.
What’s Next?
- What’s your message to Kenyans hesitant to try bitcoin, and to enthusiasts watching Bitika?
To my fellow Kenyans: bitcoin isn’t just an investment—it’s a sovereign tool. It’s money you truly own. Start small, learn, and ask questions.
To the bitcoin community: Bitika is proof that bitcoin is working in Africa. Let’s keep pushing. Let’s build tools that matter.
- How can the bitcoin community, both locally and globally, support Bitika’s mission?
We’re currently fundraising on Geyser. Support—whether it’s financial, technical, or simply sharing our story—goes a long way. Every sat you contribute helps us stay live, grow our liquidity, and continue building a tool that brings bitcoin closer to the everyday person in Africa.
Support here: https://geyser.fund/project/bitika
-
 @ b1ddb4d7:471244e7
2025-05-24 10:00:37
@ b1ddb4d7:471244e7
2025-05-24 10:00:37Custodial Lightning wallets allow users to transact without managing private keys or channel liquidity. The provider handles technical complexities, but this convenience comes with critical trade-offs:
- You don’t control your keys: The custodian holds your bitcoin.
- Centralized points of failure: Servers can be hacked or shut down.
- Surveillance risks: Providers track transaction metadata.
Key Risks of Custodial Lightning Wallets
*1. Hacks and Exit Scams*
Custodians centralize large amounts of bitcoin, attracting hackers:
- Nearly $2.2 billion worth of funds were stolen from hacks in 2024.
- Lightning custodians suffered breaches, losing user funds.
Unlike non-custodial wallets, victims have no recourse since they don’t hold keys.
*2. Censorship and Account Freezes*
Custodians comply with regulators, risking fund seizures:
- Strike (a custodial Lightning app) froze accounts of users in sanctioned regions.
- A U.K. court in 2020 ordered Bitfinex to freeze bitcoin worth $860,000 after the exchange and blockchain sleuthing firm Chainalysis traced the funds to a ransomware payment.
*3. Privacy Erosion*
Custodians log user activity, exposing sensitive data:
- Transaction amounts, receiver addresses, and IPs are recorded.
*4. Service Downtime*
Centralized infrastructure risks outages.
*5. Inflation of Lightning Network Centralization*
Custodians dominate liquidity, weakening network resilience:
- At the moment, 10% of the nodes on Lightning control 80% of the liquidity.
- This centralization contradicts bitcoin’s decentralized ethos.
How to Switch to Self-Custodial Lightning Wallets
Migrating from custodial services is straightforward:
*1. Choose a Non-Custodial Wallet*
Opt for wallets that let you control keys and channels:
- Flash: The self-custodial tool that lets you own your keys, control your coins, and transact instantly.
- Breez Wallet : Non-custodial, POS integrations.
- Core Lightning : Advanced, for self-hosted node operators.
*2. Transfer Funds Securely*
- Withdraw funds from your custodial wallet to a bitcoin on-chain address.
- Send bitcoin to your non-custodial Lightning wallet.
*3. Set Up Channel Backups*
Use tools like Static Channel Backups (SCB) to recover channels if needed.
*4. Best Practices*
- Enable Tor: Mask your IP (e.g., Breez’s built-in Tor support).
- Verify Receiving Addresses: Avoid phishing scams.
- Regularly Rebalance Channels: Use tools like Lightning Pool for liquidity.
Why Self-Custodial Lightning Matters
- Self-custody: Control your keys and funds.
- Censorship resistance: No third party can block transactions.
- Network health: Decentralized liquidity strengthens Lightning.
Self-custodial wallets now rival custodial ease.
Custodial Lightning wallets sacrifice security for convenience, putting users at risk of hacks, surveillance, and frozen funds. As bitcoin adoption grows, so does the urgency to embrace self-custodial solutions.
Take action today:
- Withdraw custodial funds to a hardware wallet.
- Migrate to a self-custodial Lightning wallet.
- Educate others on the risks of custodial control.
The Lightning Network’s potential hinges on decentralization—don’t let custodians become its Achilles’ heel.
-
 @ c1e9ab3a:9cb56b43
2025-05-09 23:10:14
@ c1e9ab3a:9cb56b43
2025-05-09 23:10:14I. Historical Foundations of U.S. Monetary Architecture
The early monetary system of the United States was built atop inherited commodity money conventions from Europe’s maritime economies. Silver and gold coins—primarily Spanish pieces of eight, Dutch guilders, and other foreign specie—formed the basis of colonial commerce. These units were already integrated into international trade and piracy networks and functioned with natural compatibility across England, France, Spain, and Denmark. Lacking a centralized mint or formal currency, the U.S. adopted these forms de facto.
As security risks and the practical constraints of physical coinage mounted, banks emerged to warehouse specie and issue redeemable certificates. These certificates evolved into fiduciary media—claims on specie not actually in hand. Banks observed over time that substantial portions of reserves remained unclaimed for years. This enabled fractional reserve banking: issuing more claims than reserves held, so long as redemption demand stayed low. The practice was inherently unstable, prone to panics and bank runs, prompting eventual centralization through the formation of the Federal Reserve in 1913.
Following the Civil War and unstable reinstatements of gold convertibility, the U.S. sought global monetary stability. After World War II, the Bretton Woods system formalized the U.S. dollar as the global reserve currency. The dollar was nominally backed by gold, but most international dollars were held offshore and recycled into U.S. Treasuries. The Nixon Shock of 1971 eliminated the gold peg, converting the dollar into pure fiat. Yet offshore dollar demand remained, sustained by oil trade mandates and the unique role of Treasuries as global reserve assets.
II. The Structure of Fiduciary Media and Treasury Demand
Under this system, foreign trade surpluses with the U.S. generate excess dollars. These surplus dollars are parked in U.S. Treasuries, thereby recycling trade imbalances into U.S. fiscal liquidity. While technically loans to the U.S. government, these purchases act like interest-only transfers—governments receive yield, and the U.S. receives spendable liquidity without principal repayment due in the short term. Debt is perpetually rolled over, rarely extinguished.
This creates an illusion of global subsidy: U.S. deficits are financed via foreign capital inflows that, in practice, function more like financial tribute systems than conventional debt markets. The underlying asset—U.S. Treasury debt—functions as the base reserve asset of the dollar system, replacing gold in post-Bretton Woods monetary logic.
III. Emergence of Tether and the Parastatal Dollar
Tether (USDT), as a private issuer of dollar-denominated tokens, mimics key central bank behaviors while operating outside the regulatory perimeter. It mints tokens allegedly backed 1:1 by U.S. dollars or dollar-denominated securities (mostly Treasuries). These tokens circulate globally, often in jurisdictions with limited banking access, and increasingly serve as synthetic dollar substitutes.
If USDT gains dominance as the preferred medium of exchange—due to technological advantages, speed, programmability, or access—it displaces Federal Reserve Notes (FRNs) not through devaluation, but through functional obsolescence. Gresham’s Law inverts: good money (more liquid, programmable, globally transferable USDT) displaces bad (FRNs) even if both maintain a nominal 1:1 parity.
Over time, this preference translates to a systemic demand shift. Actors increasingly use Tether instead of FRNs, especially in global commerce, digital marketplaces, or decentralized finance. Tether tokens effectively become shadow base money.
IV. Interaction with Commercial Banking and Redemption Mechanics
Under traditional fractional reserve systems, commercial banks issue loans denominated in U.S. dollars, expanding the money supply. When borrowers repay loans, this destroys the created dollars and contracts monetary elasticity. If borrowers repay in USDT instead of FRNs:
- Banks receive a non-Fed liability (USDT).
- USDT is not recognized as reserve-eligible within the Federal Reserve System.
- Banks must either redeem USDT for FRNs, or demand par-value conversion from Tether to settle reserve requirements and balance their books.
This places redemption pressure on Tether and threatens its 1:1 peg under stress. If redemption latency, friction, or cost arises, USDT’s equivalence to FRNs is compromised. Conversely, if banks are permitted or compelled to hold USDT as reserve or regulatory capital, Tether becomes a de facto reserve issuer.
In this scenario, banks may begin demanding loans in USDT, mirroring borrower behavior. For this to occur sustainably, banks must secure Tether liquidity. This creates two options: - Purchase USDT from Tether or on the secondary market, collateralized by existing fiat. - Borrow USDT directly from Tether, using bank-issued debt as collateral.
The latter mirrors Federal Reserve discount window operations. Tether becomes a lender of first resort, providing monetary elasticity to the banking system by creating new tokens against promissory assets—exactly how central banks function.
V. Structural Consequences: Parallel Central Banking
If Tether begins lending to commercial banks, issuing tokens backed by bank notes or collateralized debt obligations: - Tether controls the expansion of broad money through credit issuance. - Its balance sheet mimics a central bank, with Treasuries and bank debt as assets and tokens as liabilities. - It intermediates between sovereign debt and global liquidity demand, replacing the Federal Reserve’s open market operations with its own issuance-redemption cycles.
Simultaneously, if Tether purchases U.S. Treasuries with FRNs received through token issuance, it: - Supplies the Treasury with new liquidity (via bond purchases). - Collects yield on government debt. - Issues a parallel form of U.S. dollars that never require redemption—an interest-only loan to the U.S. government from a non-sovereign entity.
In this context, Tether performs monetary functions of both a central bank and a sovereign wealth fund, without political accountability or regulatory transparency.
VI. Endgame: Institutional Inversion and Fed Redundancy
This paradigm represents an institutional inversion:
- The Federal Reserve becomes a legacy issuer.
- Tether becomes the operational base money provider in both retail and interbank contexts.
- Treasuries remain the foundational reserve asset, but access to them is mediated by a private intermediary.
- The dollar persists, but its issuer changes. The State becomes a fiscal agent of a decentralized financial ecosystem, not its monetary sovereign.
Unless the Federal Reserve reasserts control—either by absorbing Tether, outlawing its instruments, or integrating its tokens into the reserve framework—it risks becoming irrelevant in the daily function of money.
Tether, in this configuration, is no longer a derivative of the dollar—it is the dollar, just one level removed from sovereign control. The future of monetary sovereignty under such a regime is post-national and platform-mediated.
-
 @ b8851a06:9b120ba1
2025-05-09 22:54:43
@ b8851a06:9b120ba1
2025-05-09 22:54:43The global financial system is creaking under its own weight. The IMF is urging banks to shore up capital, cut risk, and brace for impact. Basel III is their answer, a last-ditch effort to reinforce a brittle foundation.
But behind the scenes, a quieter revolution is under way.
Bitcoin, the world’s first stateless digital asset, is no longer on the sidelines. It’s entering the Basel conversation: not by invitation, but by inevitability.
Basel III: The System’s Self-Diagnosis
Basel III is more than a technical rulebook. It’s a confession: an admission that the global banking system is vulnerable. Created in the aftermath of 2008, it calls for: • Stronger capital reserves: So banks can survive losses. • Lower leverage: To reduce the domino effect of overexposure. • Liquidity buffers: To weather short-term shocks without collapsing.
But here’s the kicker: these rules are hostile to anything outside the fiat system. Bitcoin gets hit with a punitive 1,250% risk weight. That means for every $1 of exposure, banks must hold $1 in capital. The message from regulators? “You can hold Bitcoin, but you’ll pay for it.”
Yet that fear: based framing misses a bigger truth: Bitcoin doesn’t just survive in this environment. It thrives in it.
Bitcoin: A Parallel System, Built on Hard Rules
Where Basel III imposes “fiat discipline” from the top down, Bitcoin enforces it from the bottom up: with code, math, and transparency.
Bitcoin is not just a hedge. It’s a structural antidote to systemic fragility.
Volatility: A Strategic Asset
Yes, Bitcoin is volatile. But in a system that devalues fiat on a schedule, volatility is simply the cost of freedom. Under Basel III, banks are expected to build capital buffers during economic expansions.
What asset allows you to build those buffers faster than Bitcoin in a bull market?
When the cycle turns, those reserves act as shock absorbers: converting volatility into resilience. It’s anti-fragility in motion.
Liquidity: Real, Deep, and Global
Bitcoin settled over $19 trillion in transactions in 2024. That’s not hypothetical liquidity. it’s real, measurable flow. Unlike traditional high-quality liquid assets (HQLAs), Bitcoin is: • Available 24/7 • Borderless • Not dependent on central banks
By traditional definitions, Bitcoin is rapidly qualifying for HQLA status. Even if regulators aren’t ready to admit it.
Diversification: Breaking the Fiat Dependency
Basel III is designed to pull banks back into the fiat matrix. But Bitcoin offers an escape hatch. Strategic Bitcoin reserves are not about speculation, they’re insurance. For family offices, institutions, and sovereign funds, Bitcoin is the lifeboat when the fiat ship starts taking on water.
Regulatory Realignment: The System Reacts
The Basel Committee’s new rules on crypto exposures went live in January 2025. Around the world, regulators are scrambling to define their stance. Every new restriction placed on Bitcoin only strengthens its legitimacy, as more institutions ask: Why so much resistance, if it’s not a threat?
Bitcoin doesn’t need permission. It’s already being adopted by over 150 public companies, forward-looking states, and a new class of self-sovereign individuals.
Conclusion: The Real Question
This isn’t just about Bitcoin fitting into Basel III.
The real question is: How long can Basel III remain relevant in a world where Bitcoin exists?
Bitcoin is not the risk. It’s the reality check. And it might just be the strongest capital buffer the system has ever seen.
Gradually then suddenly.
-
 @ 5ea46480:450da5bd
2025-05-24 09:57:37
@ 5ea46480:450da5bd
2025-05-24 09:57:37Decentralization refers to control/power, and relates to censorship resistance. That is it, it is not more complicated then that. Resilience is a function of redundancy; a centralized censored system can have a redundant set-up and therefor be resilient.
Take Bitcoin; the blockchain is a central database, it is resilient because it has many redundant copies among a lot of different nodes. The message (txs and blocks) propagation is decentralized due to existence of a p2p network among these nodes, making the data distribution censorship resistant (hello op_return debate). But onchain transactions themselves are NOT p2p, they require a middlemen (a miner) because it is a central database, as opposed to something like lightning which is p2p. Peer to Peer says something about relative architectural hierarchical position/relation. P2P provides censorship resistance because it entails equal power relations, provided becoming a peer is permissionless. What makes onchain transactions censorship resistant is that mining is permissionless, and involves this open power struggle/game where competition results in a power distribution among players, meaning (hopefully) decentralization. The fact users rely on these middlemen is mitigated by this decentralization on the one hand, and temper-proofing via cryptographic signatures on the other, resulting in what we call trustlessness (or trust minimization for the autists in the room); we only rely on a miner to perform a job (including your tx into a block), but we don’t trust the miner to perform the job correctly, this we can verify ourselves.
This leads us to Nostr, because that last part is exactly what Nostr does as well. It uses cryptography to get tamper-proof messaging, which then allows you to use middle-men in a trust minimized way. The result is decentralization because in general terms, any middle man is as good as any other (same as with miners), and becoming such a middleman is permissionless(somewhat, mostly); which in turn leads to censorship resistance. It also allows for resilience because you are free to make things as redundant as you'd like.
Ergo, the crux is putting the cryptography central, making it the starting point of the system; decentralization then becomes an option due to trust minimization. The difference between Bitcoin an Nostr, is that Bitcoin maintains a global state/central ledger and needs this PoW/Nakamoto consensus fanfare; Nostr rests itself with local perspectives on 'the network'.
The problem with the Fediverse, is that it does not provide trust minimization in relation to the middlemen. Sure, there are a lot different servers, but you rely on a particular one (and the idea you could switch never really seemed to have materialized in a meaningful way). It also fails in permisionlessness because you rely on the association between servers, i.e. federation, to have meaningful access to the rest of the network. In other words, it is more a requirement of association than freedom of association; you have the freedom to be excommunicated.
The problem with ATproto is that is basically does not solve this dynamic; it only complicates it by pulling apart the components; identity and data, distribution and perspective are now separated, and supposedly you don’t rely on any particular one of these sub-component providers in the stack; but you do rely on all these different sub-component providers in the stack to play nice with each other. And this ‘playing nice’ is just the same old ‘requirement of association’ and ‘freedom of excommunication’ that looms at the horizon.
Yes, splitting up the responsibilities of identity, hosting and indexing is what is required to safe us from the platform hellscape which at this stage takes care of all three. But as it turns out, it was not a matter cutting those up into various (on paper) interchangeable middlemen. All that is required is putting cryptographic keys in the hands of the user; the tamperproofing takes care of the rest, simply by trust minimizing the middlemen we use. All the sudden it does not matter which middlemen we use, and no one is required to play nice; we lost the requirement of association, and gained freedom of association, which was the purpose of censorship resistance and therefor decentralization, to begin with.
-
 @ 21335073:a244b1ad
2025-05-09 13:56:57
@ 21335073:a244b1ad
2025-05-09 13:56:57Someone asked for my thoughts, so I’ll share them thoughtfully. I’m not here to dictate how to promote Nostr—I’m still learning about it myself. While I’m not new to Nostr, freedom tech is a newer space for me. I’m skilled at advocating for topics I deeply understand, but freedom tech isn’t my expertise, so take my words with a grain of salt. Nothing I say is set in stone.
Those who need Nostr the most are the ones most vulnerable to censorship on other platforms right now. Reaching them requires real-time awareness of global issues and the dynamic relationships between governments and tech providers, which can shift suddenly. Effective Nostr promoters must grasp this and adapt quickly.
The best messengers are people from or closely tied to these at-risk regions—those who truly understand the local political and cultural dynamics. They can connect with those in need when tensions rise. Ideal promoters are rational, trustworthy, passionate about Nostr, but above all, dedicated to amplifying people’s voices when it matters most.
Forget influencers, corporate-backed figures, or traditional online PR—it comes off as inauthentic, corny, desperate and forced. Nostr’s promotion should be grassroots and organic, driven by a few passionate individuals who believe in Nostr and the communities they serve.
The idea that “people won’t join Nostr due to lack of reach” is nonsense. Everyone knows X’s “reach” is mostly with bots. If humans want real conversations, Nostr is the place. X is great for propaganda, but Nostr is for the authentic voices of the people.
Those spreading Nostr must be so passionate they’re willing to onboard others, which is time-consuming but rewarding for the right person. They’ll need to make Nostr and onboarding a core part of who they are. I see no issue with that level of dedication. I’ve been known to get that way myself at times. It’s fun for some folks.
With love, I suggest not adding Bitcoin promotion with Nostr outreach. Zaps already integrate that element naturally. (Still promote within the Bitcoin ecosystem, but this is about reaching vulnerable voices who needed Nostr yesterday.)
To promote Nostr, forget conventional strategies. “Influencers” aren’t the answer. “Influencers” are not the future. A trusted local community member has real influence—reach them. Connect with people seeking Nostr’s benefits but lacking the technical language to express it. This means some in the Nostr community might need to step outside of the Bitcoin bubble, which is uncomfortable but necessary. Thank you in advance to those who are willing to do that.
I don’t know who is paid to promote Nostr, if anyone. This piece isn’t shade. But it’s exhausting to see innocent voices globally silenced on corporate platforms like X while Nostr exists. Last night, I wondered: how many more voices must be censored before the Nostr community gets uncomfortable and thinks creatively to reach the vulnerable?
A warning: the global need for censorship-resistant social media is undeniable. If Nostr doesn’t make itself known, something else will fill that void. Let’s start this conversation.
-
 @ a296b972:e5a7a2e8
2025-05-24 09:35:09
@ a296b972:e5a7a2e8
2025-05-24 09:35:09„Aaaach, was für ein herrlicher Tag!“
In Berlin geht man hochmotiviert an die Arbeit, in der tiefen Überzeugung stets die richtigen Entscheidungen zu treffen, die Steuern der Einzahler ausschließlich für wohlüberlegte, notwendige Investitionen auszugeben und Entscheidungen zu treffen, die im dem Umfeld, in dem man sich bewegt, als höchst sinnvoll erachtet werden. Zustimmung von allen Seiten, dann muss es ja richtig sein.
Man fährt im Dienstwagen ins Regierungsviertel, sieht die vielen geschäftigen Menschen, wie sie ebenfalls zur Arbeit eilen. Man freut sich darüber, dass alles so gut läuft, dank der überragenden Kompetenz, die man einbringen darf und die das alles ermöglicht.
In Gedanken klopft man sich auf die Schulter und sagt sich im Stillen: „Bist schon ein geiler Typ, der richtig was bewegen kann, bewegen kann.“
Man hat auch schon erkannt, dass die zunehmende Kriminalität, vorzugsweise mit einem unsachgemäß gebrauchten Messer, durch den schlechten Einfluss der sozialen Medien entstanden ist und schon entsprechende Maßnahmen auf den Weg gebracht, um das durch geleitete Meinungsäußerungen, selbstverständlich zum Wohle aller, zu unterbinden. Man ist ja nicht umsonst in diese verantwortungsvolle Position gelangt. „Endlich am Ziel!“
„Messerattacken sind unschön, unschön, aber man muss auch berücksichtigen, dass viele der Attentäter und Attentäterinnen in ihren Herkunftsländern Schlimmes erlebt haben und dadurch traumatisiert wurden. Den betroffenen Traumaopfern kann ja nichts Besseres passieren, als in eine deutsche Psychiatrie zu kommen, wo sie die allerbeste Therapie erfahren, um wieder glückliche Menschen der Gesellschaft zu werden.
** **
Und jeder, der nicht die große soziale Aufgabe erkennt, die wir uns gestellt haben und auch effizient umsetzen, muss es eben noch besser erklärt bekommen, erklärt bekommen. Daran müssen wir noch arbeiten. (Muss ich mir notieren, damit ich meinem Sekretär die Anweisung erteile, das in die Wege zu leiten). Und jeder, der sich dagegen sträubt, zeigt damit eindeutig, dass er zum rechten Rand gehört. Was denen nur einfällt? Da müssen klare Zeichen gesetzt werden, und das muss unter allen Umständen unterbunden werden, unterbunden werden.
** **
Sowas schadet der Demokratie, es delegitimiert sie“.
Zum Schutz der braven Bürger arbeitet man auch fleißig daran, Deutschland, in neuem Selbstbewusstsein, zur stärksten Kraft in Europa zu machen. Mit der Stationierung von deutschen Soldaten an der Ostfront, pardon, an der Ostflanke, zeigt man dem bösen, aggressiven Russen schon mal, was eine Harke ist. „Und das ist ja erst der Anfang, der Anfang. Warte nur ab!“
„Was noch? Ach ja, die Wirtschaft. Solange die nicht auf die Barrikaden geht, das sehe ich derzeit nicht, scheint es ja noch keinen akuten Handlungsbedarf zu geben. Darum kümmern wir uns später. Immerhin halten sich die Wirtschaftsprognosen in einem akzeptablen Rahmen und die Priorität (die kann auch nicht jeder richtig setzen) der Investitionen muss derzeit auf dem wichtigsten Bereich, der Aufrüstung liegen, Aufrüstung liegen. Schließlich werden wir bald angegriffen.
** **
Ich darf nicht vergessen, meinen Sekretär zu beauftragen, meine Bestellung im Feinkostladen abholen zu lassen, sonst gibt’s Zuhause Ärger. Ach ja, und die Anzüge und die Wäsche muss auch noch aus der Reinigung abgeholt werden. Darf ich nicht vergessen, nicht vergessen.
** **
Wie viele Reinigungen gäbe es nicht, wenn wir Politiker nicht wären, nicht wären. Viele sichere Arbeitsplätze, gut so!
** **
Was, schon da? Das ging aber heute schnell. Kein Stau. Ja, der Chauffeur ist schon ein Guter, der weiß, wo man lang muss, um Baustellen zu umfahren. Allerdings muss ich ihm bei nächster Gelegenheit noch einmal deutlich sagen, dass er bitte die Sitzheizung früher anzuschalten hat, anzuschalten hat! Dass der sich das immer noch nicht gemerkt hat, unmöglich!“
Wen wundert es, wenn in dieser Wonnewelt der Selbstüberschätzung von Unsererdemokratie gesprochen wird, so entrückt vom Alltag, in einem Raumschiff, dass völlig losgelöst von der Realität über allem schwebt.
„Ich müsste ja verrückt sein, wenn ich an diesen Zuständen etwas ändern wollte. Warum auch, es läuft doch und mir geht es doch gut. Ich habe ein gutes Einkommen, kann mir allerhand leisten, Haus ist bezahlt, Frau ist gut untergebracht, Kinder sind versorgt, wie die Zeit vergeht. Und wenn ich mal ausscheide, erhalte ich weiter meine Bezüge und muss nicht an mein Vermögen ran, man will ja auch den Kindern was hinterlassen. Schadet ja nicht, wenn ich mich etwas einschränke, und der eine oder andere Job wird schon an mich herangetragen werden, schließlich habe ich ja erstklassige Kontakte, die dem einen oder anderen sicher etwas wert sein werden.
** **
Na, dann woll’n wir mal wieder, woll’n wir mal wieder!“
Dieser Artikel wurde mit dem Pareto-Client geschrieben
* *
(Bild von pixabay)
-
 @ 1b9fc4cd:1d6d4902
2025-05-24 08:19:41
@ 1b9fc4cd:1d6d4902
2025-05-24 08:19:41Music in media is like audio umami, the perfect seasoning in a recipe. It has the ability to enhance flavor and provide depth. Daniel Siegel Alonso examines how music is indispensable in enchanting consumers, from the memorable jingles of television commercials to the emotionally charged earworms in viral videos. Its influence is ubiquitous, transforming ordinary content into unforgettable experiences, evoking emotions, and molding cultural trends.
Television Commercials: The Jingle Jungle
Siegel Alonso begins by considering the television commercial. Music is the secret weapon in advertising and marketing, where attention spans can be shorter than the length of a cat video on TikTok. With its catchy melody and simple lyrics, the classic jingle is a masterclass in auditory branding. Do you remember 1971's "I'd Like to Buy the World a Coke"? That was more than just a tune; it was a cultural touchstone.
Today, in modern advertising, music's role transcends nostalgic jingles. Brands now curate full-fledged soundtracks to build an emotional narrative. Take Apple's commercials, for example. They often spotlight indie artists whose songs capture the essence of innovation and simplicity. These choices aren't random; they align with the brand's identity and leave a lasting impression.
Music Videos: The Visual Symphony
Music videos are the perfect union of audio and visual storytelling and have revolutionized how people consume music. These clips are not merely promotional tools but are art forms. At its peak, music videos were cultural events. Nobody took advantage of the medium better than Madonna. Think of her "Justify My Love" video—a short film that was so subversive that MTV banned it. (Ever the businesswoman, The Material Girl decided to make the controversial video available commercially as a video single, marking the first time a musician released a single in this format in the United States.)
Daniel Siegel Alonso fast forwards to the current age of social media, with channels like YouTube and TikTok breathing new life into the music video. Artists can now connect directly with their audience, bypassing cautious publicists and conservative record company executives. This democratization has led to a surge in creativity. Think about Childish Gambino's cinematic "This is America." The music video sparked widespread discussion and analysis with its in-your-face imagery and complex themes. It wasn't just a song but a statement.
Social Media: The Viral Soundtrack
Music is the magical ingredient in social media that can instantly catapult content into viral fame. Platforms like TikTok have turned short, catchy music clips into a global phenomenon. A 15-second snippet can lead to myriad dance challenges, lip-sync clips, and memes, propelling relatively obscure singers to stardom overnight.
Daniel Siegel Alonso uses Lil Nas X's "Old Town Road" as a key example. With its genre-blending sound, the song became a sensation largely thanks to TikTok. Users created countless videos featuring the song, and the track's infectious energy spread like wildfire. The result was a record-breaking run on the Billboard Hot 100—and a Grammy win!
Even Instagram's Stories and Reels leverage songs to enrich their user experience. Whether it's a tearjerker ballad emphasizing heartfelt memories or an aggressive track fueling a workout video, music layers in emotional content that words and images can't achieve.
The Emotional Manipulator
Music's influence in media lies in its power to manipulate emotions—the invisible puppeteer tugs at the heartstrings, stirring nostalgia, joy, sadness, or excitement. Filmmakers and content creators understand this well. Imagine watching a horror flick without a creepy soundtrack.
In television shows, music often acts as an additional character on screen. Netflix's "Stranger Things" and HBO's "Game of Thrones" have iconic soundtracks that are instantly recognizable and have even revitalized musicians' careers (think Kate Bush and her iconic song "Running Up That Hill"). These scores aren't just background fodder; they are crucial to storytelling by creating tension and enhancing dramatic moments.
Cultural Shaper
Beyond its emotional impact, music in media also serves as a cultural shaper. It impacts everything from fashion to language and even social movements. Consider MTV's influence and reach at its height in the 1980s and 1990s. The cable channel didn't just air music videos; it created superstars and defined an era, influencing everything from hairdos to political views.
While MTV may not be the behemoth it once was, social media platforms continue the tradition today. Viral music trends can spark global discussions. For instance, the Black Lives Matter movement saw numerous musicians penning powerful anthems that became rallying cries, shared widely on social media. In this context, music transcends entertainment; it's a vehicle for evolution.
Conclusion
In the grand tapestry of media, Daniel Siegel Alonso asserts that music is the thread that weaves everything together. It turns commercials into cultural icons, music videos into visual feasts, and social media content into viral sensations. Its power to elicit emotion, contribute to culture, and tell unique stories makes it an invaluable tool for creators.
If there are stories to tell and products to sell, music will remain at the heart of media, striking the right chords and leaving an unforgettable mark on our collective psyche. Ultimately, it's not just about the notes and melodies; it's about the feelings and memories they arouse, making music the unsung hero in the ever-changing media landscape.
-
 @ 57d1a264:69f1fee1
2025-05-24 06:07:19
@ 57d1a264:69f1fee1
2025-05-24 06:07:19Definition: when every single person in the chain responsible for shipping a product looks at objectively horrendous design decisions and goes: yup, this looks good to me, release this. Designers, developers, product managers, testers, quality assurance... everyone.
I nominate Peugeot as the first example in this category.
Continue reading at https://grumpy.website/1665
https://stacker.news/items/988044
-
 @ 57d1a264:69f1fee1
2025-05-24 05:53:43
@ 57d1a264:69f1fee1
2025-05-24 05:53:43This talks highlights tools for product management, UX design, web development, and content creation to embed accessibility.
Organizations need scalability and consistency in their accessibility work, aligning people, policies, and processes to integrate it across roles. This session highlights tools for product management, UX design, web development, and content creation to embed accessibility. We will explore inclusive personas, design artifacts, design systems, and content strategies to support developers and creators, with real-world examples.
https://www.youtube.com/watch?v=-M2cMLDU4u4
https://stacker.news/items/988041
-
 @ 348e7eb2:3b0b9790
2025-05-24 05:00:33
@ 348e7eb2:3b0b9790
2025-05-24 05:00:33Nostr-Konto erstellen - funktioniert mit Hex
Was der Button macht
Der folgende Code fügt einen Button hinzu, der per Klick einen Nostr-Anmeldedialog öffnet. Alle Schritte sind im Code selbst ausführlich kommentiert.
```html
```
Erläuterungen:
- Dynamisches Nachladen: Das Script
modal.jswird nur bei Klick nachgeladen, um Fehlermeldungen beim Initial-Load zu vermeiden. -
Parameter im Überblick:
-
baseUrl: Quelle für API und Assets. an: App-Name für den Modal-Header.aa: Farbakzent (Foerbico-Farbe als Hex).al: Sprache des Interfaces.am: Licht- oder Dunkelmodus.afb/asb: Bunker-Modi für erhöhten Datenschutz.aan/aac: Steuerung der Rückgabe privater Schlüssel.arr/awr: Primal Relay als Lese- und Schreib-Relay.-
Callbacks:
-
onComplete: Schließt das Modal, zeigt eine Bestätigung und bietet die Weiterleitung zu Primal an. onCancel: Schließt das Modal und protokolliert den Abbruch.
Damit ist der gesamte Code sichtbar, kommentiert und erklärt.
- Dynamisches Nachladen: Das Script
-
 @ 06830f6c:34da40c5
2025-05-24 04:21:03
@ 06830f6c:34da40c5
2025-05-24 04:21:03The evolution of development environments is incredibly rich and complex and reflects a continuous drive towards greater efficiency, consistency, isolation, and collaboration. It's a story of abstracting away complexity and standardizing workflows.
Phase 1: The Bare Metal & Manual Era (Early 1970s - Late 1990s)
-
Direct OS Interaction / Bare Metal Development:
- Description: Developers worked directly on the operating system's command line or a basic text editor. Installation of compilers, interpreters, and libraries was a manual, often arcane process involving downloading archives, compiling from source, and setting environment variables. "Configuration drift" (differences between developer machines) was the norm.
- Tools: Text editors (Vi, Emacs), command-line compilers (GCC), Makefiles.
- Challenges: Extremely high setup time, dependency hell, "works on my machine" syndrome, difficult onboarding for new developers, lack of reproducibility. Version control was primitive (e.g., RCS, SCCS).
-
Integrated Development Environments (IDEs) - Initial Emergence:
- Description: Early IDEs (like Turbo Pascal, Microsoft Visual Basic) began to integrate editors, compilers, debuggers, and sometimes GUI builders into a single application. This was a massive leap in developer convenience.
- Tools: Turbo Pascal, Visual Basic, early Visual Studio versions.
- Advancement: Improved developer productivity, streamlined common tasks. Still relied on local system dependencies.
Phase 2: Towards Dependency Management & Local Reproducibility (Late 1990s - Mid-2000s)
-
Basic Build Tools & Dependency Resolvers (Pre-Package Managers):
- Description: As projects grew, manual dependency tracking became impossible. Tools like Ant (Java) and early versions of
autoconf/makefor C/C++ helped automate the compilation and linking process, managing some dependencies. - Tools: Apache Ant, GNU Autotools.
- Advancement: Automated build processes, rudimentary dependency linking. Still not comprehensive environment management.
- Description: As projects grew, manual dependency tracking became impossible. Tools like Ant (Java) and early versions of
-
Language-Specific Package Managers:
- Description: A significant leap was the emergence of language-specific package managers that could fetch, install, and manage libraries and frameworks declared in a project's manifest file. Examples include Maven (Java), npm (Node.js), pip (Python), RubyGems (Ruby), Composer (PHP).
- Tools: Maven, npm, pip, RubyGems, Composer.
- Advancement: Dramatically simplified dependency resolution, improved intra-project reproducibility.
- Limitation: Managed language-level dependencies, but not system-level dependencies or the underlying OS environment. Conflicts between projects on the same machine (e.g., Project A needs Python 2.7, Project B needs Python 3.9) were common.
Phase 3: Environment Isolation & Portability (Mid-2000s - Early 2010s)
-
Virtual Machines (VMs) for Development:
- Description: To address the "it works on my machine" problem stemming from OS-level and system-level differences, developers started using VMs. Tools like VMware Workstation, VirtualBox, and later Vagrant (which automated VM provisioning) allowed developers to encapsulate an entire OS and its dependencies for a project.
- Tools: VMware, VirtualBox, Vagrant.
- Advancement: Achieved strong isolation and environment reproducibility (a true "single environment" for a project).
- Limitations: Resource-heavy (each VM consumed significant CPU, RAM, disk space), slow to provision and boot, difficult to share large VM images.
-
Early Automation & Provisioning Tools:
- Description: Alongside VMs, configuration management tools started being used to automate environment setup within VMs or on servers. This helped define environments as code, making them more consistent.
- Tools: Chef, Puppet, Ansible.
- Advancement: Automated provisioning, leading to more consistent environments, often used in conjunction with VMs.
Phase 4: The Container Revolution & Orchestration (Early 2010s - Present)
-
Containerization (Docker):
- Description: Docker popularized Linux Containers (LXC), offering a lightweight, portable, and efficient alternative to VMs. Containers package an application and all its dependencies into a self-contained unit that shares the host OS kernel. This drastically reduced resource overhead and startup times compared to VMs.
- Tools: Docker.
- Advancement: Unprecedented consistency from development to production (Dev/Prod Parity), rapid provisioning, highly efficient resource use. Became the de-facto standard for packaging applications.
-
Container Orchestration:
- Description: As microservices and container adoption grew, managing hundreds or thousands of containers became a new challenge. Orchestration platforms automated the deployment, scaling, healing, and networking of containers across clusters of machines.
- Tools: Kubernetes, Docker Swarm, Apache Mesos.
- Advancement: Enabled scalable, resilient, and complex distributed systems development and deployment. The "environment" started encompassing the entire cluster.
Phase 5: Cloud-Native, Serverless & Intelligent Environments (Present - Future)
-
Cloud-Native Development:
- Description: Leveraging cloud services (managed databases, message queues, serverless functions) directly within the development workflow. Developers focus on application logic, offloading infrastructure management to cloud providers. Containers become a key deployment unit in this paradigm.
- Tools: AWS Lambda, Azure Functions, Google Cloud Run, cloud-managed databases.
- Advancement: Reduced operational overhead, increased focus on business logic, highly scalable deployments.
-
Remote Development & Cloud-Based IDEs:
- Description: The full development environment (editor, terminal, debugger, code) can now reside in the cloud, accessed via a thin client or web browser. This means developers can work from any device, anywhere, with powerful cloud resources backing their environment.
- Tools: GitHub Codespaces, Gitpod, AWS Cloud9, VS Code Remote Development.
- Advancement: Instant onboarding, consistent remote environments, access to high-spec machines regardless of local hardware, enhanced security.
-
Declarative & AI-Assisted Environments (The Near Future):
- Description: Development environments will become even more declarative, where developers specify what they need, and AI/automation tools provision and maintain it. AI will proactively identify dependency issues, optimize resource usage, suggest code snippets, and perform automated testing within the environment.
- Tools: Next-gen dev container specifications, AI agents integrated into IDEs and CI/CD pipelines.
- Prediction: Near-zero environment setup time, self-healing environments, proactive problem identification, truly seamless collaboration.
web3 #computing #cloud #devstr
-
-
 @ b04082ac:29b5c55b
2025-05-08 14:35:02
@ b04082ac:29b5c55b
2025-05-08 14:35:02Money has always been more than a medium of exchange. It reflects what societies value, how they organize trust, and what they choose to remember. This article explores the idea that money functions as a form of collective memory, and how Bitcoin may be restoring this role in a new way.

The Asante Example
In the Asante Empire, which flourished in West Africa during the 18th and 19th centuries, gold dust served as the primary medium of exchange. To measure it, traders used ornate spoons made of brass. These spoons were often carved with birds, animals, or abstract symbols. They were not currency themselves, but tools used to handle gold dust accurately.
Importantly, these spoons also carried meaning. Symbols and proverbs embedded in the spoons conveyed lessons about honesty, community, and continuity. For example, the Sankofa bird, shown turning its head backward to retrieve an egg from its back, represented the proverb, “It is not wrong to go back for that which you have forgotten.” This was a reminder to learn from the past.

The spoons reflect an understanding that money and its instruments are not just practical tools. They are cultural artifacts that store shared values. In the Asante context, even measurement was ritualized and tied to ethics and memory.
Money as a Cultural Medium
This connection between money and cultural meaning is not unique to the Asante Empire. Modern fiat currencies also carry symbols, phrases, and designs that reflect national identity and political values.
The U.S. dollar includes Latin phrases and national symbols meant to convey stability and purpose. The British pound features royal iconography, reinforcing the idea of continuity and sovereignty. When the euro was introduced, it deliberately avoided specific national references. Itsdesign used bridges and windowsto suggest openness and cooperation across the continent.

These design choices show that societies still embed meaning into their money. Even in a digital or fiat context, money is used to transmit a story about who we are, where authority lies, and what we value.
The Fragility of Fiat Memory
While fiat money carries cultural symbols, the narratives behind those symbols can be fragile.
In 2021, the central bank of the Philippines removed democratic leaders from its banknotes,triggering public criticism. In the United States, attempts to replace Andrew Jackson with Harriet Tubman on the $20 billfaced repeated delays. These examples show how political control over money includes control over what stories are told and remembered.

Unlike objects passed down through generations, fiat memory can be edited or erased. In this sense, it is vulnerable. The meaning encoded in fiat systems can shift depending on who holds power.
Bitcoin as a New Form of Memory
Bitcoin is described as digital money. But it also introduces a different model of how societies can record value and preserve meaning.
The Bitcoin network launched in 2009 with a small message embedded in its first block: “Chancellor on brink of second bailout for banks.” This was a reference to a newspaper headline that day and a clear sign of protest against financial bailouts, centralized monetary policy, and forever wars.

This moment marked the beginning of a system where memory is stored differently. Instead of relying on governments or institutions, Bitcoin stores its history on a public ledger maintained by a decentralized network of participants. Its memory is not symbolic or political; it is structural. Every transaction, every block, is preserved through time-stamped computation and consensus.
No single authority can change it. The rules are clear and publicly auditable. In this way, Bitcoin offers a version of money where memory is both neutral and resilient.
Cultural Expression and Community Values
Even though Bitcoin lacks the traditional symbols found on banknotes, it has developed its own culture. Phrases like “Don’t trust, verify” or “Stay humble, stack sats” are shared widely in the Bitcoin community. These ideas reflect a focus on self-responsibility, verification, and long-term thinking.
These proverbs can be compared to the carved messages on the Asante spoons. While the contexts are very different, the underlying idea is similar: a community using language and symbols to reinforce its shared values.
Bitcoin also has a well established and growing art scene. Bitcoin conferences often feature dedicated sections for art inspired by the protocol and its culture. Statues of Satoshi Nakamoto have been installed in cities like Budapest, Lugano, and Fornelli. These physical works reflect the desire to link Bitcoin’s abstract values to something tangible.

Looking Back to Look Forward
The Asante example helps us see that money has long been tied to memory and meaning. Their spoons were practical tools but also cultural anchors. Bitcoin, while new and digital, may be playing a similar role.
Instead of relying on political symbols or national myths, Bitcoin uses code, transparency, and global consensus to create trust. In doing so, it offers a way to preserve economic memory that does not depend on power or politics.
It’s still early to know what kind of legacy Bitcoin will leave. But if it succeeds, it may not just change how money works. It may also change how civilizations remember.
-
 @ 90152b7f:04e57401
2025-05-24 03:47:24
@ 90152b7f:04e57401
2025-05-24 03:47:24"Army study suggests U.S. force of 20,000"
The Washington Times - Friday, April 5, 2002
The Bush administration says there are no active plans to put American peacekeepers between Palestinians and Israelis, but at least one internal military study says 20,000 well-armed troops would be needed.
The Army’s School of Advanced Military Studies (SAMS), an elite training ground and think tank at Fort Leavenworth, Kan., produced the study last year. The 68-page paper tells how the major operation would be run the first year, with peacekeepers stationed in Gaza, Hebron, Jerusalem and Nablus.
One major goal would be to “neutralize leadership of Palestine dissenting factions [and] prevent inter-Palestinian violence.”
The military is known to update secret contingency plans in the event international peacekeepers are part of a comprehensive Middle East peace plan. The SAMS study, a copy of which was obtained by The Washington Times, provides a glimpse of what those plans might entail.
Defense Secretary Donald H. Rumsfeld repeatedly has said the administration has no plans to put American troops between the warring factions. But since the escalation of violence, more voices in the debate are beginning to suggest that some type of American-led peace enforcement team is needed.
Sen. Arlen Specter, Pennsylvania Republican, quoted U.S. special envoy Gen. Anthony Zinni as saying there is a plan, if needed, to put a limited number of American peacekeepers in the Israeli-occupied territories.
Asked on CBS whether he could envision American troops on the ground, Mr. Specter said Sunday: “If we were ever to stabilize the situation, and that was a critical factor, it’s something that I would be willing to consider.”
Added Sen. Joseph R. Biden Jr., Delaware Democrat and Senate Foreign Relations Committee chairman, “In that context, yes, and with European forces as well.”
The recent history of international peacekeeping has shown that it often takes American firepower and prestige for the operation to work. The United Nations made futile attempts to stop Serbian attacks on the Muslim population in Bosnia.
The U.S. entered the fray by bombing Serbian targets and bringing about a peace agreement that still is being backed up by American soldiers on the ground. U.S. combat troops are also in Kosovo, and they have a more limited role in Macedonia.
But James Phillips, a Middle East analyst at the Heritage Foundation, used the word “disaster” to describe the aftermath of putting an international force in the occupied territories.
“I think that would be a formula for sucking us into the violence,” he said. “United States troops would be a lightening rod for attacks by radical Islamics and other Palestinian extremist groups. The United States cannot afford to stretch its forces any thinner. They’re very busy as it is with the war against international terrorism.”
Mr. Phillips noted that two Norwegian observers in Hebron were killed this week. U.N. representatives on the Lebanon border have been unable to prevent terrorists from attacking Israel.
The SAMS paper tries to predict events in the first year of peacekeeping and the dangers U.S. troops would face.
It calls the Israeli armed forces a “500-pound gorilla in Israel. Well armed and trained. Operates in both Gaza [and the West Bank]. Known to disregard international law to accomplish mission. Very unlikely to fire on American forces.”
On the Mossad, the Israeli intelligence service, the Army study says, “Wildcard. Ruthless and cunning. Has capability to target U.S. forces and make it look like a Palestinian/Arab act.”
It described Palestinian youth as “loose cannons; under no control, sometimes violent.” The study was done by 60 officers dubbed the “Jedi Knights,” as all second-year SAMS students are called. The Times first reported on their work in September. Recent violence in the Middle East has raised questions about what type of force it would take to keep the peace.
In the past, SAMS has done studies for the Army chief of staff and the Joint Chiefs. SAMS personnel helped plan the allied ground attack that liberated Kuwait.
The Middle East study sets goals that a peace force should accomplish in the first 30 days. They include “create conditions for development of Palestinian State and security of [Israel],” ensure “equal distribution of contract value or equivalent aid” and “build lasting relationships based on new legal borders and not religious-territorial claims.”
The SAMS report does not specify a full order of battle for the 20,000 troops. An Army source who reviewed the paper said each of three brigades would require about 100 armored vehicles, 25 tanks and 12 self-propelled howitzers, along with attack helicopters and spy drones.
The Palestinians have supported calls for an international force, but Tel Aviv has opposed the idea.
https://www.washingtontimes.com/news/2002/apr/5/20020405-041726-2086r/
-
 @ 40bdcc08:ad00fd2c
2025-05-06 14:24:22
@ 40bdcc08:ad00fd2c
2025-05-06 14:24:22Introduction
Bitcoin’s
OP_RETURNopcode, a mechanism for embedding small data in transactions, has ignited a significant debate within the Bitcoin community. Originally designed to support limited metadata while preserving Bitcoin’s role as a peer-to-peer electronic cash system,OP_RETURNis now at the center of proposals that could redefine Bitcoin’s identity. The immutable nature of Bitcoin’s timechain makes it an attractive platform for data storage, creating tension with those who prioritize its monetary function. This discussion, particularly around Bitcoin Core pull request #32406 (GitHub PR #32406), highlights a critical juncture for Bitcoin’s future.What is
OP_RETURN?Introduced in 2014,
OP_RETURNallows users to attach up to 80 bytes of data to a Bitcoin transaction. Unlike other transaction outputs,OP_RETURNoutputs are provably unspendable, meaning they don’t burden the Unspent Transaction Output (UTXO) set—a critical database for Bitcoin nodes. This feature was a compromise to provide a standardized, less harmful way to include metadata, addressing earlier practices that embedded data in ways that bloated the UTXO set. The 80-byte limit and restriction to oneOP_RETURNoutput per transaction are part of Bitcoin Core’s standardness rules, which guide transaction relay and mining but are not enforced by the network’s consensus rules (Bitcoin Stack Exchange).Standardness vs. Consensus Rules
Standardness rules are Bitcoin Core’s default policies for relaying and mining transactions. They differ from consensus rules, which define what transactions are valid across the entire network. For
OP_RETURN: - Consensus Rules: AllowOP_RETURNoutputs with data up to the maximum script size (approximately 10,000 bytes) and multiple outputs per transaction (Bitcoin Stack Exchange). - Standardness Rules: LimitOP_RETURNdata to 80 bytes and one output per transaction to discourage excessive data storage and maintain network efficiency.Node operators can adjust these policies using settings like
-datacarrier(enables/disablesOP_RETURNrelay) and-datacarriersize(sets the maximum data size, defaulting to 83 bytes to account for theOP_RETURNopcode and pushdata byte). These settings allow flexibility but reflect Bitcoin Core’s default stance on limiting data usage.The Proposal: Pull Request #32406
Bitcoin Core pull request #32406, proposed by developer instagibbs, seeks to relax these standardness restrictions (GitHub PR #32406). Key changes include: - Removing Default Size Limits: The default
-datacarriersizewould be uncapped, allowing largerOP_RETURNdata without a predefined limit. - Allowing Multiple Outputs: The restriction to oneOP_RETURNoutput per transaction would be lifted, with the total data size across all outputs subject to a configurable limit. - Deprecating Configuration Options: The-datacarrierand-datacarriersizesettings are marked as deprecated, signaling potential removal in future releases, which could limit node operators’ ability to enforce custom restrictions.This proposal does not alter consensus rules, meaning miners and nodes can already accept transactions with larger or multiple
OP_RETURNoutputs. Instead, it changes Bitcoin Core’s default relay policy to align with existing practices, such as miners accepting non-standard transactions via services like Marathon Digital’s Slipstream (CoinDesk).Node Operator Flexibility
Currently, node operators can customize
OP_RETURNhandling: - Default Settings: Relay transactions with oneOP_RETURNoutput up to 80 bytes. - Custom Settings: Operators can disableOP_RETURNrelay (-datacarrier=0) or adjust the size limit (e.g.,-datacarriersize=100). These options remain in #32406 but are deprecated, suggesting that future Bitcoin Core versions might not support such customization, potentially standardizing the uncapped policy.Arguments in Favor of Relaxing Limits
Supporters of pull request #32406 and similar proposals argue that the current restrictions are outdated and ineffective. Their key points include: - Ineffective Limits: Developers bypass the 80-byte limit using methods like Inscriptions, which store data in other transaction parts, often at higher cost and inefficiency (BitcoinDev Mailing List). Relaxing
OP_RETURNcould channel data into a more efficient format. - Preventing UTXO Bloat: By encouragingOP_RETURNuse, which doesn’t affect the UTXO set, the proposal could reduce reliance on harmful alternatives like unspendable Taproot outputs used by projects like Citrea’s Clementine bridge. - Supporting Innovation: Projects like Citrea require more data (e.g., 144 bytes) for security proofs, and relaxed limits could enable new Layer 2 solutions (CryptoSlate). - Code Simplification: Developers like Peter Todd argue that these limits complicate Bitcoin Core’s codebase unnecessarily (CoinGeek). - Aligning with Practice: Miners already process non-standard transactions, and uncapping defaults could improve fee estimation and reduce reliance on out-of-band services, as noted by ismaelsadeeq in the pull request discussion.In the GitHub discussion, developers like Sjors and TheCharlatan expressed support (Concept ACK), citing these efficiency and innovation benefits.
Arguments Against Relaxing Limits
Opponents, including prominent developers and community members, raise significant concerns about the implications of these changes: - Deviation from Bitcoin’s Purpose: Critics like Luke Dashjr, who called the proposal “utter insanity,” argue that Bitcoin’s base layer should prioritize peer-to-peer cash, not data storage (CoinDesk). Jason Hughes warned it could turn Bitcoin into a “worthless altcoin” (BeInCrypto). - Blockchain Bloat: Additional data increases the storage and processing burden on full nodes, potentially making node operation cost-prohibitive and threatening decentralization (CryptoSlate). - Network Congestion: Unrestricted data could lead to “spam” transactions, raising fees and hindering Bitcoin’s use for financial transactions. - Risk of Illicit Content: The timechain’s immutability means data, including potentially illegal or objectionable content, is permanently stored on every node. The 80-byte limit acts as a practical barrier, and relaxing it could exacerbate this issue. - Preserving Consensus: Developers like John Carvalho view the limits as a hard-won community agreement, not to be changed lightly.
In the pull request discussion, nsvrn and moth-oss expressed concerns about spam and centralization, advocating for gradual changes. Concept NACKs from developers like wizkid057 and Luke Dashjr reflect strong opposition.
Community Feedback
The GitHub discussion for pull request #32406 shows a divided community: - Support (Concept ACK): Sjors, polespinasa, ismaelsadeeq, miketwenty1, TheCharlatan, Psifour. - Opposition (Concept NACK): wizkid057, BitcoinMechanic, Retropex, nsvrn, moth-oss, Luke Dashjr. - Other: Peter Todd provided a stale ACK, indicating partial or outdated support.
Additional discussions on the BitcoinDev mailing list and related pull requests (e.g., #32359 by Peter Todd) highlight similar arguments, with #32359 proposing a more aggressive removal of all
OP_RETURNlimits and configuration options (GitHub PR #32359).| Feedback Type | Developers | Key Points | |---------------|------------|------------| | Concept ACK | Sjors, ismaelsadeeq, others | Improves efficiency, supports innovation, aligns with mining practices. | | Concept NACK | Luke Dashjr, wizkid057, others | Risks bloat, spam, centralization, and deviation from Bitcoin’s purpose. | | Stale ACK | Peter Todd | Acknowledges proposal but with reservations or outdated support. |
Workarounds and Their Implications
The existence of workarounds, such as Inscriptions, which exploit SegWit discounts to embed data, is a key argument for relaxing
OP_RETURNlimits. These methods are costlier and less efficient, often costing more thanOP_RETURNfor data under 143 bytes (BitcoinDev Mailing List). Supporters argue that formalizing largerOP_RETURNdata could streamline these use cases. Critics, however, see workarounds as a reason to strengthen, not weaken, restrictions, emphasizing the need to address underlying incentives rather than accommodating bypasses.Ecosystem Pressures
External factors influence the debate: - Miners: Services like Marathon Digital’s Slipstream process non-standard transactions for a fee, showing that market incentives already bypass standardness rules. - Layer 2 Projects: Citrea’s Clementine bridge, requiring more data for security proofs, exemplifies the demand for relaxed limits to support innovative applications. - Community Dynamics: The debate echoes past controversies, like the Ordinals debate, where data storage via inscriptions raised similar concerns about Bitcoin’s purpose (CoinDesk).
Bitcoin’s Identity at Stake
The
OP_RETURNdebate is not merely technical but philosophical, questioning whether Bitcoin should remain a focused monetary system or evolve into a broader data platform. Supporters see relaxed limits as a pragmatic step toward efficiency and innovation, while opponents view them as a risk to Bitcoin’s decentralization, accessibility, and core mission. The community’s decision will have lasting implications, affecting node operators, miners, developers, and users.Conclusion
As Bitcoin navigates this crossroads, the community must balance the potential benefits of relaxed
OP_RETURNlimits—such as improved efficiency and support for new applications—against the risks of blockchain bloat, network congestion, and deviation from its monetary roots. The ongoing discussion, accessible via pull request #32406 on GitHub (GitHub PR #32406). Readers are encouraged to explore the debate and contribute to ensuring that any changes align with Bitcoin’s long-term goals as a decentralized, secure, and reliable system. -
 @ 2b998b04:86727e47
2025-05-24 03:40:36
@ 2b998b04:86727e47
2025-05-24 03:40:36Solzhenitsyn Would Have Loved Bitcoin
I didn’t plan to write this. But a comment from @HODL stirred something in me — a passing thought that took root and wouldn’t let go:
> “Solzhenitsyn would have understood Bitcoin.”
The more I sat with it, the more I realized: he wouldn’t have just understood it — he would have loved it.
A Life of Resistance
Aleksandr Solzhenitsyn didn’t just survive the Soviet gulags — he exposed them. Through The Gulag Archipelago and other works, he revealed the quiet machinery of evil: not always through brutality, but through systemic lies, suppressed memory, and coerced consensus.
His core belief was devastatingly simple:
> “The line dividing good and evil cuts through the heart of every human being.”
He never let anyone off the hook — not the state, not the system, not even himself. Evil, to Solzhenitsyn, was not “out there.” It was within. And resisting it required truth, courage, and deep personal responsibility.
Bitcoin: Truth That Resists
That’s why I believe Solzhenitsyn would have resonated with Bitcoin.
Not the hype. Not the coins. Not the influencers.
But the heart of it:
-
A system that resists coercion.
-
A ledger that cannot be falsified.
-
A network that cannot be silenced.
-
A protocol that doesn't care about party lines — only proof of work.
Bitcoin is incorruptible memory.\ Solzhenitsyn fought to preserve memory in the face of state erasure.\ Bitcoin cannot forget — and it cannot be made to lie.
Responsibility and Sovereignty
Bitcoin demands what Solzhenitsyn demanded: moral responsibility. You hold your keys. You verify your truth. You cannot delegate conscience.
He once wrote:
> “A man who is not inwardly prepared for the use of violence against him is always weaker than his opponent.”
Bitcoin flips that equation. It gives the peaceful man a weapon: truth that cannot be seized.
I’ve Felt This Line Too
I haven’t read all of The Gulag Archipelago — it’s long, and weighty — but I’ve read enough to know Solzhenitsyn’s voice. And I’ve felt the line he describes:
> That dividing line between good and evil… that runs through my own heart.
That’s why I left the noise of Web3. That’s why I’m building with Bitcoin. Because I believe the moral architecture of this protocol matters. It forces me to live in alignment — or walk away.
Final Word
I think Solzhenitsyn would have seen Bitcoin not as a tech innovation, but as a moral stand. Not a replacement for Christ — but a quiet echo of His justice.
And that’s why I keep stacking, writing, building — one block at a time.
Written with help from ChatGPT (Dr. C), and inspired by a comment from @HODL that sparked something deep.
If this resonated, feel free to zap a few sats — not because I need them, but because signal flows best when it’s shared with intention.
HODL mentioned this idea in a note — their Primal profile:\ https://primal.net/hodl
-
-
 @ 58537364:705b4b85
2025-05-24 03:25:05
@ 58537364:705b4b85
2025-05-24 03:25:05Ep 228 "วิชาชีวิต"
คนเราเมื่อเกิดมาแล้ว ไม่ได้หวังแค่มีชีวิตรอดเท่านั้น แต่ยังปรารถนา "ความเจริญก้าวหน้า" และ "ความสุขในชีวิต"
จึงพากันศึกษาเล่าเรียนเพื่อให้มี "วิชาความรู้" สำหรับการประกอบอาชีพ โดยเชื่อว่า การงานที่มั่นคงย่อมนำ "ความสำเร็จ" และ "ความเจริญก้าวหน้า" มาให้
อย่างไรก็ตาม...ความสำเร็จในวิชาชีพหรือความเจริญก้าวหน้าในชีวิต ไม่ได้เป็นหลักประกันความสุขอย่างแท้จริง
แม้เงินทองและทรัพย์สมบัติจะช่วยให้ชีวิตมีความสุข สะดวก สบาย แต่ไม่ได้ช่วยให้สุขใจในสิ่งที่ตนมี หากยังรู้สึกว่า "ตนยังมีไม่พอ"
ขณะเดียวกันชื่อเสียงเกียรติยศที่ได้มาก็ไม่ช่วยให้คลายความทุกข์ใจ เมื่อต้องเผชิญปัญหาต่างๆ นาๆ
ทั้งการพลัดพราก การสูญเสียบุคคลผู้เป็นที่รัก ความเจ็บป่วย และความตายที่ต้องเกิดขึ้นกับทุกคน
ยิ่งกว่านั้น...ความสำเร็จในอาชีพและความเจริญก้าวหน้าในชีวิต ล้วนเป็น "สิ่งไม่เที่ยง" แปรผันตกต่ำ ไม่สามารถควบคุมได้
วิชาชีพทั้งหลายช่วยให้เราหาเงินได้มากขึ้น แต่ไม่ได้ช่วยให้เราเข้าถึง "ความสุขที่แท้จริง"
คนที่ประสบความสำเร็จในวิชาชีพไม่น้อย ที่มีชีวิตอมทุกข์ ความเครียดรุมเร้า สุขภาพเสื่อมโทรม
หากเราไม่อยากเผชิญกับสิ่งเหล่านี้ ควรเรียน "วิชาชีวิต" เพื่อเข้าใจโลก เข้าใจชีวิต รู้เท่าทันความผันแปรไปของสรรพสิ่ง
วิชาชีวิต...เรียนจากประสบการณ์ชีวิต เมื่อมีปัญหาต่างๆ ขอให้คิดว่า คือ "บททดสอบ"
จงหมั่นศึกษาหาบทเรียนจากวิชานี้อยู่เสมอ สร้าง "ความตระหนักรู้" ถึงความสำคัญในการมีชีวิต
ช่วงที่ผ่านมา เมื่อมีปัญหาฉันไม่สามารถหาทางออกจากทุกข์ได้เศร้า เสียใจ ทุรน ทุราย สอบตก "วิชาชีวิต"
โชคดีครูบาอาจารย์ให้ข้อคิด กล่าวว่า เป็นเรื่องธรรมดาหากเรายังไม่เข้าใจชีวิต ทุกสิ่งล้วนผันแปร เกิด-ดับ เป็นธรรมดา ท่านเมตตาส่งหนังสือเล่มนี้มาให้
เมื่อค่อยๆ ศึกษา ทำความเข้าใจ นำความทุกข์ที่เกิดขึ้นมาพิจารณา เห็นว่าเมื่อ "สอบตก" ก็ "สอบใหม่" จนกว่าจะผ่านไปได้
วิชาทางโลกเมื่อสอบตกยังเปิดโอกาสให้เรา "สอบซ่อม" วิชาทางธรรมก็เช่นเดียวกัน หากเจอปัญหา อุปสรรค หรือ ความทุกข์ถาโถมเข้ามา ขอให้เราตั้งสติ ว่า จะตั้งใจทำข้อสอบนี้ให้ผ่านไปให้จงได้
หากเราสามารถดำเนินชีวิตด้วยความเข้าใจ เราจะค้นพบ "วิชาชีวิต" ที่สามารถทำให้หลุดพ้นจากความทุกข์ได้แน่นอน
ด้วยรักและปรารถนาดี ปาริชาติ รักตะบุตร 21 เมษายน 2566
น้อมกราบขอบพระคุณพระ อ.ไพศาล วิสาโล เป็นอย่างสูง ที่ท่านเมตตา ให้ข้อธรรมะยามทุกข์ใจและส่งหนังสือมาให้ จึงตั้งใจอยากแบ่งปันเป็นธรรมทาน
-
 @ d61f3bc5:0da6ef4a
2025-05-06 01:37:28
@ d61f3bc5:0da6ef4a
2025-05-06 01:37:28I remember the first gathering of Nostr devs two years ago in Costa Rica. We were all psyched because Nostr appeared to solve the problem of self-sovereign online identity and decentralized publishing. The protocol seemed well-suited for textual content, but it wasn't really designed to handle binary files, like images or video.
The Problem
When I publish a note that contains an image link, the note itself is resilient thanks to Nostr, but if the hosting service disappears or takes my image down, my note will be broken forever. We need a way to publish binary data without relying on a single hosting provider.
We were discussing how there really was no reliable solution to this problem even outside of Nostr. Peer-to-peer attempts like IPFS simply didn't work; they were hopelessly slow and unreliable in practice. Torrents worked for popular files like movies, but couldn't be relied on for general file hosting.
Awesome Blossom
A year later, I attended the Sovereign Engineering demo day in Madeira, organized by Pablo and Gigi. Many projects were presented over a three hour demo session that day, but one really stood out for me.
Introduced by hzrd149 and Stu Bowman, Blossom blew my mind because it showed how we can solve complex problems easily by simply relying on the fact that Nostr exists. Having an open user directory, with the corresponding social graph and web of trust is an incredible building block.
Since we can easily look up any user on Nostr and read their profile metadata, we can just get them to simply tell us where their files are stored. This, combined with hash-based addressing (borrowed from IPFS), is all we need to solve our problem.
How Blossom Works
The Blossom protocol (Blobs Stored Simply on Mediaservers) is formally defined in a series of BUDs (Blossom Upgrade Documents). Yes, Blossom is the most well-branded protocol in the history of protocols. Feel free to refer to the spec for details, but I will provide a high level explanation here.
The main idea behind Blossom can be summarized in three points:
- Users specify which media server(s) they use via their public Blossom settings published on Nostr;
- All files are uniquely addressable via hashes;
- If an app fails to load a file from the original URL, it simply goes to get it from the server(s) specified in the user's Blossom settings.
Just like Nostr itself, the Blossom protocol is dead-simple and it works!
Let's use this image as an example:
 If you look at the URL for this image, you will notice that it looks like this:
If you look at the URL for this image, you will notice that it looks like this:blossom.primal.net/c1aa63f983a44185d039092912bfb7f33adcf63ed3cae371ebe6905da5f688d0.jpgAll Blossom URLs follow this format:
[server]/[file-hash].[extension]The file hash is important because it uniquely identifies the file in question. Apps can use it to verify that the file they received is exactly the file they requested. It also gives us the ability to reliably get the same file from a different server.
Nostr users declare which media server(s) they use by publishing their Blossom settings. If I store my files on Server A, and they get removed, I can simply upload them to Server B, update my public Blossom settings, and all Blossom-capable apps will be able to find them at the new location. All my existing notes will continue to display media content without any issues.
Blossom Mirroring
Let's face it, re-uploading files to another server after they got removed from the original server is not the best user experience. Most people wouldn't have the backups of all the files, and/or the desire to do this work.
This is where Blossom's mirroring feature comes handy. In addition to the primary media server, a Blossom user can set one one or more mirror servers. Under this setup, every time a file is uploaded to the primary server the Nostr app issues a mirror request to the primary server, directing it to copy the file to all the specified mirrors. This way there is always a copy of all content on multiple servers and in case the primary becomes unavailable, Blossom-capable apps will automatically start loading from the mirror.
Mirrors are really easy to setup (you can do it in two clicks in Primal) and this arrangement ensures robust media handling without any central points of failure. Note that you can use professional media hosting services side by side with self-hosted backup servers that anyone can run at home.
Using Blossom Within Primal
Blossom is natively integrated into the entire Primal stack and enabled by default. If you are using Primal 2.2 or later, you don't need to do anything to enable Blossom, all your media uploads are blossoming already.
To enhance user privacy, all Primal apps use the "/media" endpoint per BUD-05, which strips all metadata from uploaded files before they are saved and optionally mirrored to other Blossom servers, per user settings. You can use any Blossom server as your primary media server in Primal, as well as setup any number of mirrors:
 ## Conclusion
## ConclusionFor such a simple protocol, Blossom gives us three major benefits:
- Verifiable authenticity. All Nostr notes are always signed by the note author. With Blossom, the signed note includes a unique hash for each referenced media file, making it impossible to falsify.
- File hosting redundancy. Having multiple live copies of referenced media files (via Blossom mirroring) greatly increases the resiliency of media content published on Nostr.
- Censorship resistance. Blossom enables us to seamlessly switch media hosting providers in case of censorship.
Thanks for reading; and enjoy! 🌸
-
 @ 2b998b04:86727e47
2025-05-24 03:16:38
@ 2b998b04:86727e47
2025-05-24 03:16:38Most of the assets I hold—real estate, equities, and businesses—depreciate in value over time. Some literally, like physical buildings and equipment. Some functionally, like tech platforms that age faster than they grow. Even cash, which should feel "safe," quietly loses ground to inflation. Yet I continue to build. I continue to hold. And I continue to believe that what I’m doing matters.
But underneath all of that — beneath the mortgages, margin trades, and business pivots — I’ve made a long-term bet:
Bitcoin will outlast the decay.
The Decaying System I Still Operate In
Let me be clear: I’m not a Bitcoin purist. I use debt. I borrow to acquire real estate. I trade with margin in a brokerage account. I understand leverage — not as a sin, but as a tool that must be used with precision and respect. But I’m also not naive.
The entire fiat-based financial system is built on a slow erosion of value. Inflation isn't a bug — it’s a feature. And it's why most business models, whether in real estate or retail, implicitly rely on asset inflation just to stay solvent.
That’s not sustainable. And it’s not honest.
The Bitcoin Thesis: Deflation That Works for You
Bitcoin is fundamentally different. Its supply is fixed. Its issuance is decreasing. Over time, as adoption grows and fiat weakens, Bitcoin’s purchasing power increases.
That changes the game.
If you can hold even a small portion of your balance sheet in BTC — not just as an investment, but as a strategic hedge — it becomes a way to offset the natural depreciation of your other holdings. Your buildings may age. Your cash flow may fluctuate. But your Bitcoin, if properly secured and held with conviction, becomes the anchor.
It’s not about day trading BTC or catching the next ATH. It’s about understanding that in a world designed to leak value, Bitcoin lets you patch the hole.
Why This Matters for Builders
If you run a business — especially one with real assets, recurring costs, or thin margins — you know how brutal depreciation can be. Taxes, maintenance, inflation, replacement cycles… it never stops.
Adding BTC to your long-term treasury isn’t about becoming a "crypto company." It’s about becoming anti-fragile. It’s about building with a component that doesn’t rot.
In 5, 10, or 20 years, I may still be paying off mortgages and navigating property cycles. But if my Bitcoin allocation is still intact, still growing in real purchasing power… then I haven’t just preserved wealth. I’ve preserved optionality. I’ve created a counterbalance to the relentless decay of everything else.
Final Word
I still play the fiat game — because for now, I have to. But I’m no longer betting everything on it. Bitcoin is my base layer now. Quiet, cold-stored, and uncompromising.
It offsets depreciation — not just financially, but philosophically. It reminds me that not everything has to erode. Not everything has to be sacrificed to time or policy or inflation.
Some things can actually hold. Some things can last.
And if I build right — maybe what I build can last too.
If this resonated, feel free to send a zap — it helps me keep writing and building from a place of conviction.
This article was co-written with the help of ChatGPT, a tool I use to refine and clarify what I’m working through in real time.
-
 @ 502ab02a:a2860397
2025-05-24 01:14:43
@ 502ab02a:a2860397
2025-05-24 01:14:43ในสายตาคนรักสุขภาพทั่วโลก “อโวคาโด” คือผลไม้ในฝัน มันมีไขมันดี มีไฟเบอร์สูง ช่วยลดคอเลสเตอรอลได้ มีวิตามินอี มีโพแทสเซียม และที่สำคัญคือ "ดูดี" ทุกครั้งที่ถูกปาดวางบนขนมปังโฮลวีตในชามสลัด หรือบนโฆษณาอาหารคลีนสุดหรู
แต่ในสายตาชาวไร่บางคนในเม็กซิโกหรือชุมชนพื้นเมืองในโดมินิกัน อโวคาโดไม่ใช่ผลไม้แห่งสุขภาพ แต่มันคือสัญลักษณ์ของความรุนแรง การกดขี่ และการสูญเสียเสรีภาพในผืนดินของตัวเอง
เมื่ออาหารกลายเป็นทองคำ กลุ่มอิทธิพลก็ไม่เคยพลาดจะเข้าครอบครอง
เรามักได้ยินคำว่า "ทองคำเขียว" หรือ Green Gold ใช้เรียกอโวคาโด เพราะในรอบ 20 ปีที่ผ่านมา ความต้องการบริโภคของมันพุ่งสูงขึ้นเป็นเท่าตัว โดยเฉพาะในสหรัฐฯ และยุโรป จากผลการวิจัยของมหาวิทยาลัยฮาร์วาร์ดและข้อมูลการส่งออกของ USDA พบว่า 90% ของอโวคาโดที่บริโภคในอเมริกา มาจากรัฐมิโชอากังของเม็กซิโก พื้นที่ซึ่งควบคุมโดยกลุ่มค้ายาเสพติดไม่ต่างจากเจ้าของสวนตัวจริง
พวกเขาเรียกเก็บ “ค่าคุ้มครอง” จากเกษตรกร โดยใช้วิธีเดียวกับมาเฟีย คือ ถ้าไม่จ่าย ก็เจ็บตัวหรือหายตัว ไม่ว่าจะเป็นกลุ่ม CJNG (Jalisco New Generation Cartel), Familia Michoacana หรือ Caballeros Templarios พวกเขาไม่ได้สนใจว่าใครปลูกหรือใครรดน้ำ ตราบใดที่ผลผลิตสามารถเปลี่ยนเป็นเงินได้
องค์กรอาชญากรรมเหล่านี้ไม่ได้แค่ “แฝงตัว” ในอุตสาหกรรม แต่ ยึดครอง ห่วงโซ่การผลิตทั้งหมด ตั้งแต่แปลงปลูกไปจนถึงโรงบรรจุและเส้นทางขนส่ง คนที่ไม่ยอมเข้าระบบมืดอาจต้องพบจุดจบในป่า หรือไม่มีชื่ออยู่ในทะเบียนบ้านอีกต่อไป
จากรายงานของเว็บไซต์ Food is Power องค์กรไม่แสวงกำไรด้านความยุติธรรมด้านอาหารในสหรัฐฯ เผยว่า ในปี 2020 มีเกษตรกรในเม็กซิโกจำนวนมากที่ถูกข่มขู่ บางรายถึงขั้นถูกฆาตกรรม เพราะปฏิเสธจ่ายค่าคุ้มครองจากกลุ่มค้ายา
การปลูกอโวคาโดไม่ใช่เรื่องเบาๆ กับธรรมชาติ เพราะมันต้องการ “น้ำ” มากถึง 272 ลิตรต่อผลเดียว! เรามาดูว่า “272 ลิตร” นี้ เท่ากับอะไรบ้างในชีวิตจริง อาบน้ำฝักบัวนาน 10–12 นาที (โดยเฉลี่ยใช้น้ำ 20–25 ลิตรต่อนาที) ใช้น้ำซักเสื้อผ้าเครื่องหนึ่ง (เครื่องซักผ้า 1 ครั้งกินประมาณ 60–100 ลิตร) น้ำดื่มของคนหนึ่งคนได้นานเกือบ เดือน (คนเราต้องการน้ำดื่มประมาณ 1.5–2 ลิตรต่อวัน)
ถ้าเราใช้ข้อมูลจาก FAO และ Water Footprint Network การผลิตเนื้อวัว 1 กิโลกรัม ต้องใช้น้ำ 15,000 ลิตร (รวมทั้งการปลูกหญ้า อาหารสัตว์ การดื่มน้ำของวัว ฯลฯ) ได้โปรตีนราว 250 กรัม อโวคาโด 1 กิโลกรัม (ราว 5 ผล) ใช้น้ำประมาณ 1,360 ลิตร ได้โปรตีนเพียง 6–8 กรัมเท่านั้น พูดง่ายๆคือ เมื่อเทียบอัตราส่วนเป็นลิตรต่อกรัมโปรตีนแล้วนั้น วัวใช้น้ำ 60 ลิตรต่อกรัมโปรตีน / อโวคาโด ใช้น้ำ 194 ลิตรต่อกรัมโปรตีน แถมการเลี้ยงวัวในระบบธรรมชาติ (เช่น pasture-raised หรือ regenerative farming) ยังสามารถเป็นส่วนหนึ่งของระบบหมุนเวียนน้ำและคาร์บอนได้ พอเห็นภาพแล้วใช่ไหมครับ ดังนั้นเราควรระมัดระวังการเสพสื่อเอาไว้ด้วยว่า คำว่า "ดีต่อโลก" ไม่ได้หมายถึงพืชอย่างเดียว ทุกธุรกิจถ้าทำแบบที่ควรทำ มันยังสามารถผลักดันโลกไม่ให้ตกอยู่ในมือองค์กร future food ได้ เพราะมูลค่ามันสูงมาก
และเมื่อราคาสูง พื้นที่เพาะปลูกก็ขยายอย่างไร้การควบคุม ป่าธรรมชาติในรัฐมิโชอากังถูกแอบโค่นแบบผิดกฎหมายเพื่อแปลงสภาพเป็นไร่ “ทองเขียว” ข้อมูลจาก Reuters พบว่าผลไม้ที่ถูกส่งออกไปยังสหรัฐฯ บางส่วนมาจากแปลงปลูกที่บุกรุกป่าคุ้มครอง และรัฐบาลเองก็ไม่สามารถควบคุมได้เพราะอิทธิพลของกลุ่มทุนและมาเฟีย
ในโดมินิกันก็เช่นกัน มีรายงานจากสำนักข่าว Gestalten ว่าพื้นที่ป่าสงวนหลายพันไร่ถูกเปลี่ยนเป็นไร่อโวคาโด เพื่อป้อนตลาดผู้บริโภคในอเมริกาและยุโรปโดยตรง โดยไม่มีการชดเชยใดๆ แก่ชุมชนท้องถิ่น
สุขภาพที่ดีไม่ควรได้มาจากการทำลายสุขภาพของคนอื่น ไม่ควรมีผลไม้ใดที่ดูดีในจานของเรา แล้วเบื้องหลังเต็มไปด้วยคราบเลือดและน้ำตาของคนปลูก
เฮียไม่ได้จะบอกให้เลิกกินอโวคาโดเลย แต่เฮียอยากให้เรารู้ทัน ว่าความนิยมของอาหารสุขภาพวันนี้ กำลังเป็นสนามใหม่ของกลุ่มทุนโลก ที่พร้อมจะครอบครองด้วย “อำนาจอ่อน” ผ่านแบรนด์อาหารธรรมชาติ ผ่านกฎหมายสิ่งแวดล้อม หรือแม้แต่การครอบงำตลาดเสรีด้วยกำลังอาวุธ
นี่ไม่ใช่เรื่องไกลตัว เพราะเมื่อกลุ่มทุนเริ่มฮุบเมล็ดพันธุ์ คุมเส้นทางขนส่ง คุมฉลาก Certified Organic ทั้งหลาย พวกเขาก็ “ควบคุมสุขภาพ” ของผู้บริโภคเมืองอย่างเราไปด้วยโดยอ้อม
คำถามสำคัญที่มาทุกครั้งเวลามีเนื้อหาอะไรมาฝากคือ แล้วเราจะทำอะไรได้? 555555 - เลือกบริโภคผลไม้จากแหล่งที่โปร่งใสหรือปลูกเองได้ - สนับสนุนเกษตรกรรายย่อยที่ไม่อยู่ภายใต้กลุ่มทุน - ใช้เสียงของผู้บริโภคกดดันให้มีระบบตรวจสอบต้นทางจริง ไม่ใช่แค่ฉลากเขียวสวยๆ - และที่สำคัญ อย่าเชื่อว่า “ทุกสิ่งที่เขาวางให้ดูสุขภาพดี” จะดีจริง (ข้อนี่ละตัวดีเลยครับ)
สุขภาพไม่ใช่สินค้า และอาหารไม่ควรเป็นอาวุธของกลุ่มทุน หากเราเริ่มตระหนักว่าอาหารคือการเมือง น้ำคืออำนาจ และแปลงเกษตรคือสนามรบ เฮียเชื่อว่าผู้บริโภคอย่างเราจะไม่ยอมเป็นหมากอีกต่อไป #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ f7d424b5:618c51e8
2025-05-04 19:19:43
@ f7d424b5:618c51e8
2025-05-04 19:19:43Listen to the new episode here!
Finally some good news. Good new games, worthwhile remakes, and bloggers facing the consequences of their actions. Gaming is healing. Let's talk about it!
Stuff cited:
Obligatory:
- Discuss this episode on OUR NEW FORUM
- Get the RSS and Subscribe (this is a new feed URL, but the old one redirects here too!)
- Get a modern podcast app to use that RSS feed on at newpodcastapps.com
- Or listen to the show on the forum using the embedded Podverse player!
- Send your complaints here
Reminder that this is a Value4Value podcast so any support you can give us via a modern podcasting app is greatly appreciated and we will never bow to corporate sponsors!
-
 @ 52b4a076:e7fad8bd
2025-05-03 21:54:45
@ 52b4a076:e7fad8bd
2025-05-03 21:54:45Introduction
Me and Fishcake have been working on infrastructure for Noswhere and Nostr.build. Part of this involves processing a large amount of Nostr events for features such as search, analytics, and feeds.
I have been recently developing
nosdexv3, a newer version of the Noswhere scraper that is designed for maximum performance and fault tolerance using FoundationDB (FDB).Fishcake has been working on a processing system for Nostr events to use with NB, based off of Cloudflare (CF) Pipelines, which is a relatively new beta product. This evening, we put it all to the test.
First preparations
We set up a new CF Pipelines endpoint, and I implemented a basic importer that took data from the
nosdexdatabase. This was quite slow, as it did HTTP requests synchronously, but worked as a good smoke test.Asynchronous indexing
I implemented a high-contention queue system designed for highly parallel indexing operations, built using FDB, that supports: - Fully customizable batch sizes - Per-index queues - Hundreds of parallel consumers - Automatic retry logic using lease expiration
When the scraper first gets an event, it will process it and eventually write it to the blob store and FDB. Each new event is appended to the event log.
On the indexing side, a
Queuerwill read the event log, and batch events (usually 2K-5K events) into one work job. This work job contains: - A range in the log to index - Which target this job is intended for - The size of the job and some other metadataEach job has an associated leasing state, which is used to handle retries and prioritization, and ensure no duplication of work.
Several
Workers monitor the index queue (up to 128) and wait for new jobs that are available to lease.Once a suitable job is found, the worker acquires a lease on the job and reads the relevant events from FDB and the blob store.
Depending on the indexing type, the job will be processed in one of a number of ways, and then marked as completed or returned for retries.
In this case, the event is also forwarded to CF Pipelines.
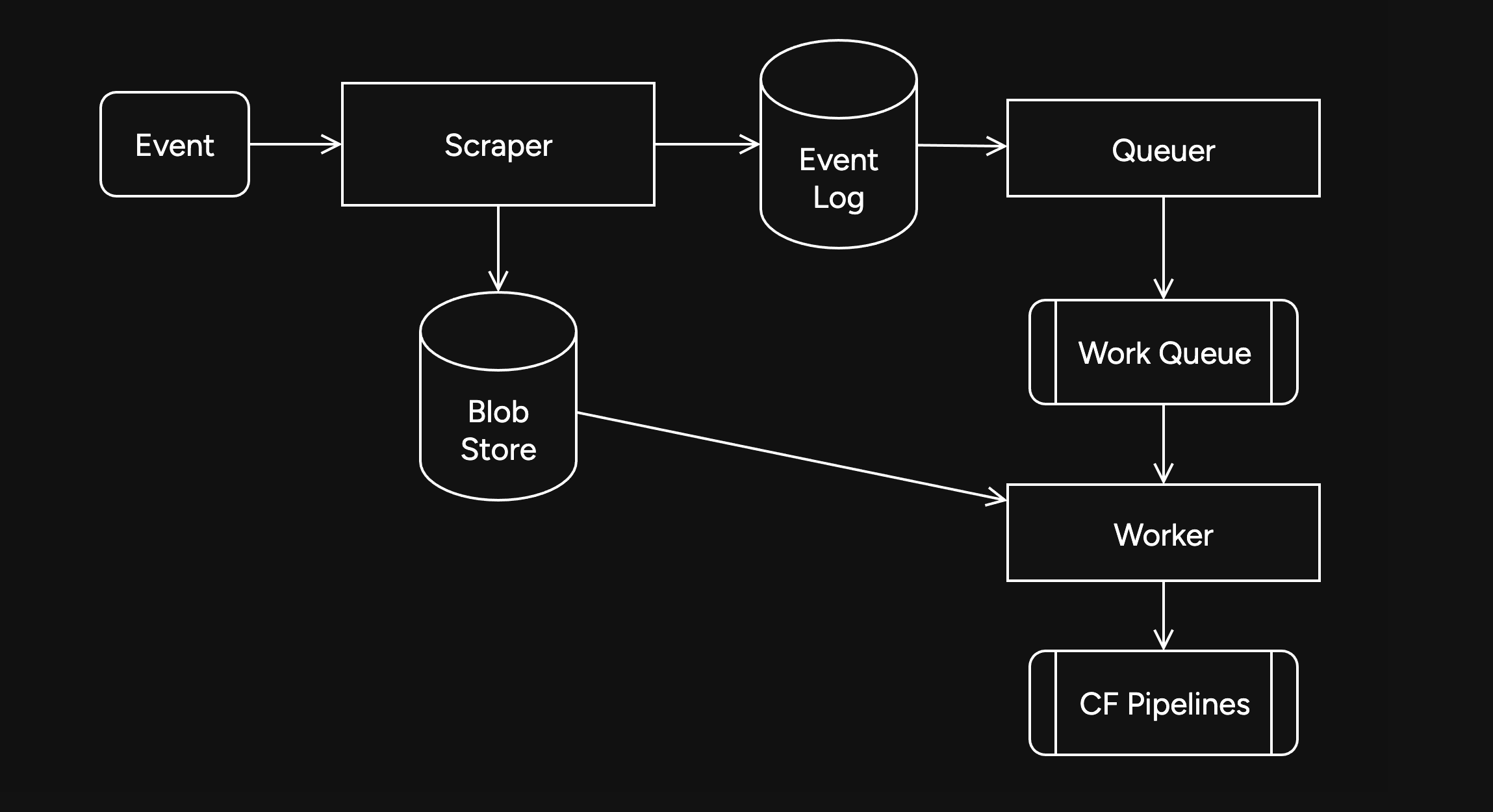
Trying it out
The first attempt did not go well. I found a bug in the high-contention indexer that led to frequent transaction conflicts. This was easily solved by correcting an incorrectly set parameter.
We also found there were other issues in the indexer, such as an insufficient amount of threads, and a suspicious decrease in the speed of the
Queuerduring processing of queued jobs.Along with fixing these issues, I also implemented other optimizations, such as deprioritizing
WorkerDB accesses, and increasing the batch size.To fix the degraded
Queuerperformance, I ran the backfill job by itself, and then started indexing after it had completed.Bottlenecks, bottlenecks everywhere

After implementing these fixes, there was an interesting problem: The DB couldn't go over 80K reads per second. I had encountered this limit during load testing for the scraper and other FDB benchmarks.
As I suspected, this was a client thread limitation, as one thread seemed to be using high amounts of CPU. To overcome this, I created a new client instance for each
Worker.After investigating, I discovered that the Go FoundationDB client cached the database connection. This meant all attempts to create separate DB connections ended up being useless.
Using
OpenWithConnectionStringpartially resolved this issue. (This also had benefits for service-discovery based connection configuration.)To be able to fully support multi-threading, I needed to enabled the FDB multi-client feature. Enabling it also allowed easier upgrades across DB versions, as FDB clients are incompatible across versions:
FDB_NETWORK_OPTION_EXTERNAL_CLIENT_LIBRARY="/lib/libfdb_c.so"FDB_NETWORK_OPTION_CLIENT_THREADS_PER_VERSION="16"Breaking the 100K/s reads barrier
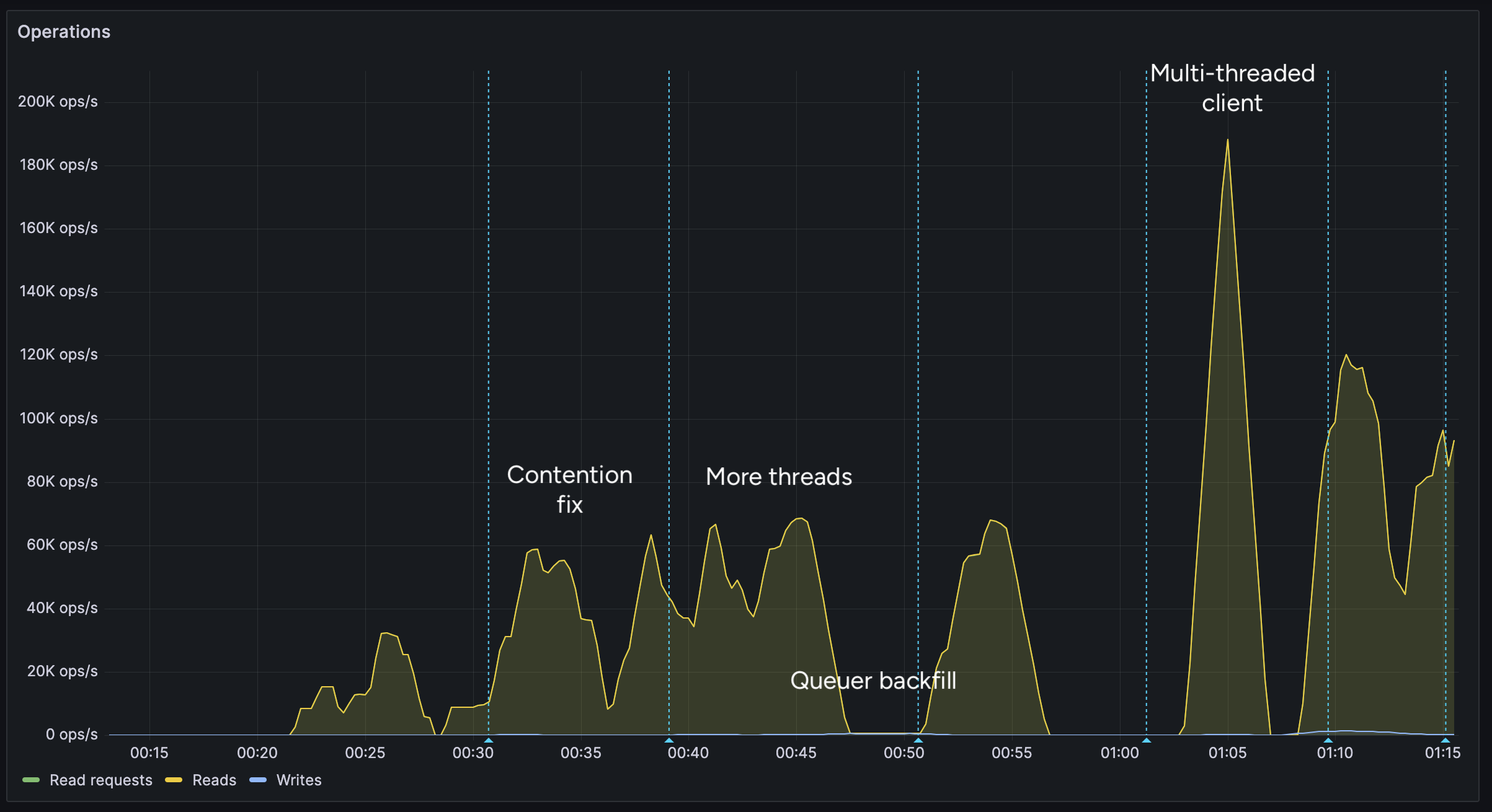
After implementing support for the multi-threaded client, we were able to get over 100K reads per second.
You may notice after the restart (gap) the performance dropped. This was caused by several bugs: 1. When creating the CF Pipelines endpoint, we did not specify a region. The automatically selected region was far away from the server. 2. The amount of shards were not sufficient, so we increased them. 3. The client overloaded a few HTTP/2 connections with too many requests.
I implemented a feature to assign each
Workerits own HTTP client, fixing the 3rd issue. We also moved the entire storage region to West Europe to be closer to the servers.After these changes, we were able to easily push over 200K reads/s, mostly limited by missing optimizations:
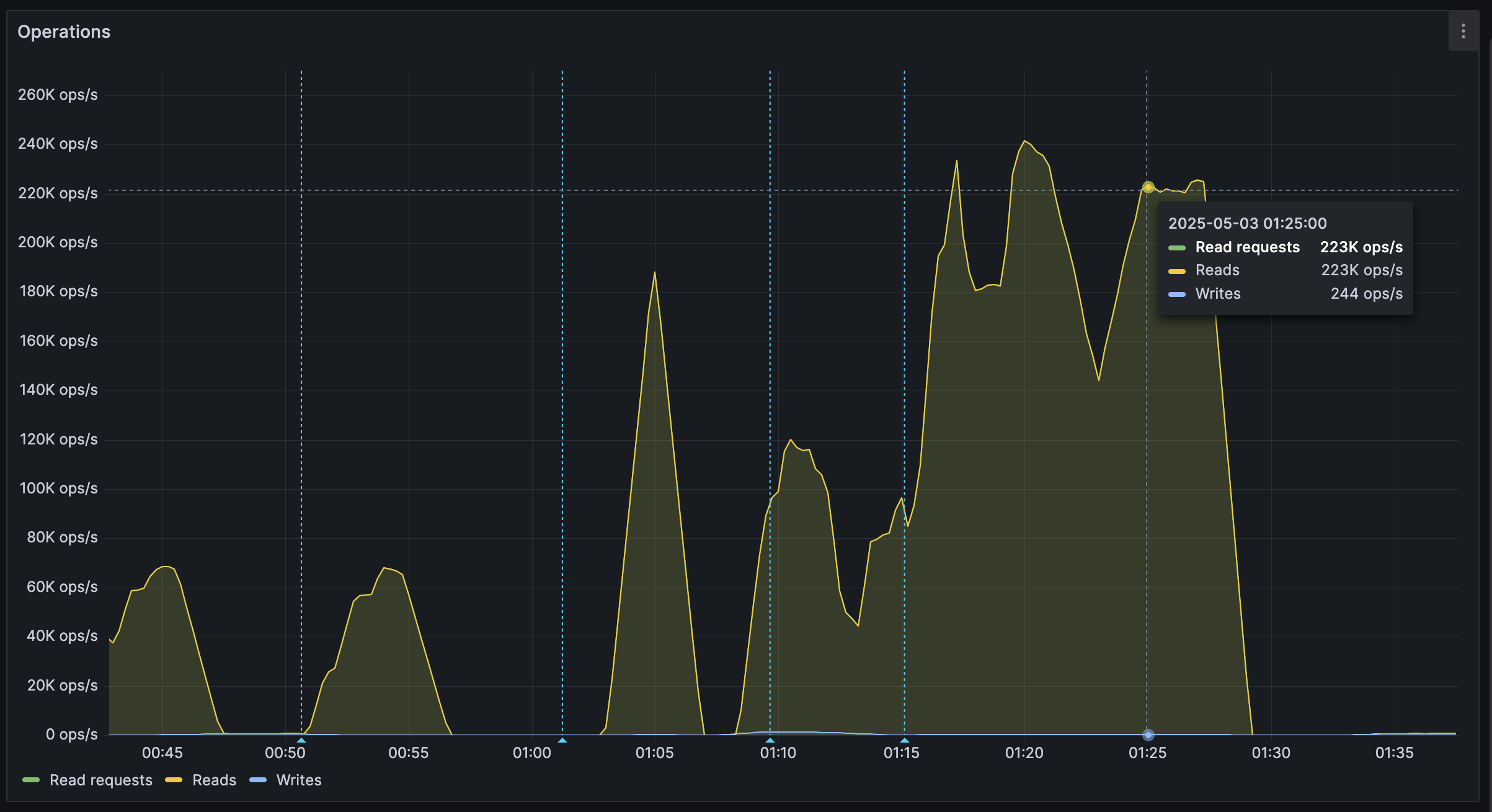
It's shards all the way down
While testing, we also noticed another issue: At certain times, a pipeline would get overloaded, stalling requests for seconds at a time. This prevented all forward progress on the
Workers.We solved this by having multiple pipelines: A primary pipeline meant to be for standard load, with moderate batching duration and less shards, and high-throughput pipelines with more shards.
Each
Workeris assigned a pipeline on startup, and if one pipeline stalls, other workers can continue making progress and saturate the DB.The stress test
After making sure everything was ready for the import, we cleared all data, and started the import.
The entire import lasted 20 minutes between 01:44 UTC and 02:04 UTC, reaching a peak of: - 0.25M requests per second - 0.6M keys read per second - 140MB/s reads from DB - 2Gbps of network throughput
FoundationDB ran smoothly during this test, with: - Read times under 2ms - Zero conflicting transactions - No overloaded servers
CF Pipelines held up well, delivering batches to R2 without any issues, while reaching its maximum possible throughput.

Finishing notes
Me and Fishcake have been building infrastructure around scaling Nostr, from media, to relays, to content indexing. We consistently work on improving scalability, resiliency and stability, even outside these posts.
Many things, including what you see here, are already a part of Nostr.build, Noswhere and NFDB, and many other changes are being implemented every day.
If you like what you are seeing, and want to integrate it, get in touch. :)
If you want to support our work, you can zap this post, or register for nostr.land and nostr.build today.
-
 @ d0aa74cd:603d35cd
2025-05-03 10:55:11
@ d0aa74cd:603d35cd
2025-05-03 10:55:11CLI #Haskell
https://photonsphere.org/post/2025-05-03-command-line-energy-prices-haskell/
-
 @ 90152b7f:04e57401
2025-05-23 23:38:49
@ 90152b7f:04e57401
2025-05-23 23:38:49WikiLeaks The Global Intelligence Files
Released on 2013-03-04 00:00 GMT
| Email-ID | 296467 | | -------- | -------------------------- | | Date | 2007-10-29 20:54:22 | | From | <hrwpress@hrw.org> | | To | <responses@stratfor.com> |
Gaza: Israel's Fuel and Power Cuts Violate Laws of War\ \ For Immediate Release\ \ Gaza: Israel's Fuel and Power Cuts Violate Laws of War\ \ Civilians Should Not Be Penalized for Rocket Attacks by Armed Groups\ \ (New York, October 29, 2007) - Israel's decision to limit fuel and\ electricity to the Gaza Strip in retaliation for unlawful rocket attacks\ by armed groups amounts to collective punishment against the civilian\ population of Gaza, in violation of international law, and will worsen the\ humanitarian crisis there, Human Rights Watch said today.\ \ "Israel may respond to rocket attacks by armed groups to protect its\ population, but only in lawful ways," said Sarah Leah Whitson, director of\ Human Rights Watch's Middle East division. "Because Israel remains an\ occupying power, in light of its continuing restrictions on Gaza, Israel\ must not take measures that harm the civilian population - yet that is\ precisely what cutting fuel or electricity for even short periods will\ do."\ \ On Sunday, the Israeli Defense Ministry ordered the reduction of fuel\ shipments from Israel to Gaza. A government spokesman said the plan was to\ cut the amount of fuel by 5 to 11 percent without affecting the supply of\ industrial fuel for Gaza's only power plant.\ \ According to Palestinian officials, fuel shipments into Gaza yesterday\ fell by more than 30 percent.\ \ In response to the government's decision, a group of 10 Palestinian and\ Israeli human rights groups petitioned the Israeli Supreme Court on\ Sunday, seeking an immediate injunction against the fuel and electricity\ cuts. The court gave the government five days to respond but did not issue\ a temporary injunction. On Monday, the groups requested an urgent hearing\ before the five days expire.\ \ Last Thursday, Defense Minister Ehud Barak approved cutting electricity to\ Gaza for increasing periods in response to ongoing rocket attacks against\ civilian areas in Israel, but the government has not yet implemented the\ order.\ \ The rockets fired by Palestinian armed groups violate the international\ legal prohibition on indiscriminate attacks because they are highly\ inaccurate and cannot be directed at a specific target. Because Hamas\ exercises power inside Gaza, it is responsible for stopping indiscriminate\ attacks even when carried out by other groups, Human Rights Watch said.\ \ On Friday, Israeli Prime Minister Ehud Olmert said that Israel would\ respond strongly to the ongoing attacks without allowing a humanitarian\ crisis. But the UN's top humanitarian official, UN Deputy\ Secretary-General John Holmes, said that a "serious humanitarian crisis"\ in Gaza already exists, and called on Israel to lift the economic blockade\ that it tightened after Hamas seized power in June.\ \ Israel's decision to cut fuel and electricity is the latest move aimed\ ostensibly against Hamas that is affecting the entire population of Gaza.\ In September, the Israeli cabinet declared Gaza "hostile territory" and\ voted to "restrict the passage of various goods to the Gaza Strip and\ reduce the supply of fuel and electricity." Since then, Israel has\ increasingly blocked supplies into Gaza, letting in limited amounts of\ essential foodstuffs, medicine and humanitarian supplies. According to\ Holmes, the number of humanitarian convoys entering Gaza had dropped to\ 1,500 in September from 3,000 in July.\ \ "Cutting fuel and electricity obstructs vital services," Whitson said.\ "Operating rooms, sewage pumps, and water well pumps all need electricity\ to run."\ \ Israel sells to Gaza roughly 60 percent of the electricity consumed by the\ territory's 1.5 million inhabitants. In June 2006, six Israeli missiles\ struck Gaza's only power plant; today, for most residents, electricity is\ available during only limited hours.\ \ Israeli officials said they would cut electricity for 15 minutes after\ each rocket attack and then for increasingly longer periods if the attacks\ persist. Deputy Defense Minister Matan Vilnai said Israel would\ "dramatically reduce" the power it supplied to Gaza over a period of\ weeks.\ \ Cutting fuel or electricity to the civilian population violates a basic\ principle of international humanitarian law, or the laws of war, which\ prohibit a government that has effective control over a territory from\ attacking or withholding objects that are essential to the survival of the\ civilian population. Such an act would also violate Israel's duty as an\ occupying power to safeguard the health and welfare of the population\ under occupation.\ \ Israel withdrew its military forces and settlers from the Gaza Strip in\ 2005. Nonetheless, Israel remains responsible for ensuring the well-being\ of Gaza's population for as long as, and to the extent that, it retains\ effective control over the area. Israel still exercises control over\ Gaza's airspace, sea space and land borders, as well as its electricity,\ water, sewage and telecommunications networks and population registry.\ Israel can and has also reentered Gaza for security operations at will.\ \ Israeli officials state that by declaring Gaza "hostile territory," it is\ no longer obliged under international law to supply utilities to the\ civilian population, but that is a misstatement of the law.\ \ "A mere declaration does not change the facts on the ground that impose on\ Israel the status and obligations of an occupying power," said Whitson.\ \ For more information, please contact:\ \ In New York, Fred Abrahams (English, German): +1-917-385-7333 (mobile)\ \ In Washington, DC, Joe Stork (English): +1-202-299-4925 (mobile)\ \ In Cairo, Gasser Abdel-Razek (Arabic, English): +20-2-2-794-5036 (mobile);\ or +20-10-502-9999 (mobile)
-
 @ 34f1ddab:2ca0cf7c
2025-05-23 23:15:14
@ 34f1ddab:2ca0cf7c
2025-05-23 23:15:14Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ 2183e947:f497b975
2025-05-01 22:33:48
@ 2183e947:f497b975
2025-05-01 22:33:48Most darknet markets (DNMs) are designed poorly in the following ways:
1. Hosting
Most DNMs use a model whereby merchants fill out a form to create their listings, and the data they submit then gets hosted on the DNM's servers. In scenarios where a "legal" website would be forced to censor that content (e.g. a DMCA takedown order), DNMs, of course, do not obey. This can lead to authorities trying to find the DNM's servers to take enforcement actions against them. This design creates a single point of failure.
A better design is to outsource hosting to third parties. Let merchants host their listings on nostr relays, not on the DNM's server. The DNM should only be designed as an open source interface for exploring listings hosted elsewhere, that way takedown orders end up with the people who actually host the listings, i.e. with nostr relays, and not with the DNM itself. And if a nostr relay DOES go down due to enforcement action, it does not significantly affect the DNM -- they'll just stop querying for listings from that relay in their next software update, because that relay doesn't work anymore, and only query for listings from relays that still work.
2. Moderation
Most DNMs have employees who curate the listings on the DNM. For example, they approve/deny listings depending on whether they fit the content policies of the website. Some DNMs are only for drugs, others are only for firearms. The problem is, to approve a criminal listing is, in the eyes of law enforcement, an act of conspiracy. Consequently, they don't just go after the merchant who made the listing but the moderators who approved it, and since the moderators typically act under the direction of the DNM, this means the police go after the DNM itself.
A better design is to outsource moderation to third parties. Let anyone call themselves a moderator and create lists of approved goods and services. Merchants can pay the most popular third party moderators to add their products to their lists. The DNM itself just lets its users pick which moderators to use, such that the user's choice -- and not a choice by the DNM -- determines what goods and services the user sees in the interface.
That way, the police go after the moderators and merchants rather than the DNM itself, which is basically just a web browser: it doesn't host anything or approve of any content, it just shows what its users tell it to show. And if a popular moderator gets arrested, his list will still work for a while, but will gradually get more and more outdated, leading someone else to eventually become the new most popular moderator, and a natural transition can occur.
3. Escrow
Most DNMs offer an escrow solution whereby users do not pay merchants directly. Rather, during the Checkout process, they put their money in escrow, and request the DNM to release it to the merchant when the product arrives, otherwise they initiate a dispute. Most DNMs consider escrow necessary because DNM users and merchants do not trust one another; users don't want to pay for a product first and then discover that the merchant never ships it, and merchants don't want to ship a product first and then discover that the user never pays for it.
The problem is, running an escrow solution for criminals is almost certain to get you accused of conspiracy, money laundering, and unlicensed money transmission, so the police are likely to shut down any DNM that does this. A better design is to oursource escrow to third parties. Let anyone call themselves an escrow, and let moderators approve escrows just like they approve listings. A merchant or user who doesn't trust the escrows chosen by a given moderator can just pick a different moderator. That way, the police go after the third party escrows rather than the DNM itself, which never touches user funds.
4. Consequences
Designing a DNM along these principles has an interesting consequence: the DNM is no longer anything but an interface, a glorified web browser. It doesn't host any content, approve any listings, or touch any money. It doesn't even really need a server -- it can just be an HTML file that users open up on their computer or smart phone. For two reasons, such a program is hard to take down:
First, it is hard for the police to justify going after the DNM, since there are no charges to bring. Its maintainers aren't doing anything illegal, no more than Firefox does anything illegal by maintaining a web browser that some people use to browse illegal content. What the user displays in the app is up to them, not to the code maintainers. Second, if the police decided to go after the DNM anyway, they still couldn't take it down because it's just an HTML file -- the maintainers do not even need to run a server to host the file, because users can share it with one another, eliminating all single points of failure.
Another consequence of this design is this: most of the listings will probably be legal, because there is more demand for legal goods and services than illegal ones. Users who want to find illegal goods would pick moderators who only approve those listings, but everyone else would use "legal" moderators, and the app would not, at first glance, look much like a DNM, just a marketplace for legal goods and services. To find the illegal stuff that lurks among the abundant legal stuff, you'd probably have to filter for it via your selection of moderators, making it seem like the "default" mode is legal.
5. Conclusion
I think this DNM model is far better than the designs that prevail today. It is easier to maintain, harder to take down, and pushes the "hard parts" to the edges, so that the DNM is not significantly affected even if a major merchant, moderator, or escrow gets arrested. I hope it comes to fruition.
-
 @ c1e9ab3a:9cb56b43
2025-05-01 17:29:18
@ c1e9ab3a:9cb56b43
2025-05-01 17:29:18High-Level Overview
Bitcoin developers are currently debating a proposed change to how Bitcoin Core handles the
OP_RETURNopcode — a mechanism that allows users to insert small amounts of data into the blockchain. Specifically, the controversy revolves around removing built-in filters that limit how much data can be stored using this feature (currently capped at 80 bytes).Summary of Both Sides
Position A: Remove OP_RETURN Filters
Advocates: nostr:npub1ej493cmun8y9h3082spg5uvt63jgtewneve526g7e2urca2afrxqm3ndrm, nostr:npub12rv5lskctqxxs2c8rf2zlzc7xx3qpvzs3w4etgemauy9thegr43sf485vg, nostr:npub17u5dneh8qjp43ecfxr6u5e9sjamsmxyuekrg2nlxrrk6nj9rsyrqywt4tp, others
Arguments: - Ineffectiveness of filters: Filters are easily bypassed and do not stop spam effectively. - Code simplification: Removing arbitrary limits reduces code complexity. - Permissionless innovation: Enables new use cases like cross-chain bridges and timestamping without protocol-level barriers. - Economic regulation: Fees should determine what data gets added to the blockchain, not protocol rules.
Position B: Keep OP_RETURN Filters
Advocates: nostr:npub1lh273a4wpkup00stw8dzqjvvrqrfdrv2v3v4t8pynuezlfe5vjnsnaa9nk, nostr:npub1s33sw6y2p8kpz2t8avz5feu2n6yvfr6swykrnm2frletd7spnt5qew252p, nostr:npub1wnlu28xrq9gv77dkevck6ws4euej4v568rlvn66gf2c428tdrptqq3n3wr, others
Arguments: - Historical intent: Satoshi included filters to keep Bitcoin focused on monetary transactions. - Resource protection: Helps prevent blockchain bloat and abuse from non-financial uses. - Network preservation: Protects the network from being overwhelmed by low-value or malicious data. - Social governance: Maintains conservative changes to ensure long-term robustness.
Strengths and Weaknesses
Strengths of Removing Filters
- Encourages decentralized innovation.
- Simplifies development and maintenance.
- Maintains ideological purity of a permissionless system.
Weaknesses of Removing Filters
- Opens the door to increased non-financial data and potential spam.
- May dilute Bitcoin’s core purpose as sound money.
- Risks short-term exploitation before economic filters adapt.
Strengths of Keeping Filters
- Preserves Bitcoin’s identity and original purpose.
- Provides a simple protective mechanism against abuse.
- Aligns with conservative development philosophy of Bitcoin Core.
Weaknesses of Keeping Filters
- Encourages central decision-making on allowed use cases.
- Leads to workarounds that may be less efficient or obscure.
- Discourages novel but legitimate applications.
Long-Term Consequences
If Filters Are Removed
- Positive: Potential boom in new applications, better interoperability, cleaner architecture.
- Negative: Risk of increased blockchain size, more bandwidth/storage costs, spam wars.
If Filters Are Retained
- Positive: Preserves monetary focus and operational discipline.
- Negative: Alienates developers seeking broader use cases, may ossify the protocol.
Conclusion
The debate highlights a core philosophical split in Bitcoin: whether it should remain a narrow monetary system or evolve into a broader data layer for decentralized applications. Both paths carry risks and tradeoffs. The outcome will shape not just Bitcoin's technical direction but its social contract and future role in the broader crypto ecosystem.
-
 @ 6c05c73e:c4356f17
2025-05-23 22:59:35
@ 6c05c73e:c4356f17
2025-05-23 22:59:35Como a grande maioria dos brasileiros. Eu não comecei um negócio porque “queria empreender”. Diferente disso, eu PRECISAVA para poder pagar contas e manter o básico.
Festas, openbar e camisas
Meu primeiro negócio foi na verdade um combo. Eu tinha saído do último trampo e eu gostava de festas. Então, comecei a organizar uma festa mensalmente na casa do meu pai. Eu pagava a água, energia e dava uma grana para ele. Em troca, organizava festa de sábado para domingo open bar.
A fórmula era simples. Criava o evento da festa no facebook, convidava todo mundo que conhecia. Panfletava na cidade e espalhava cartazes nos pontos de ônibus sobre a festa. E, para fechar com chave de ouro. Mulher era OFF até 20:00. Consequência? Os caras vinham e pagavam o ingresso deles e delas. Kkkkk. E, enchia…
Comecei a notar que a galera se vestia mal. E, pensei: "Porque não vestir eles?” Pimba! Comecei a desenha e confeccionar camisas para vender nas festas. E, pimba denovo! Vendeu, tudo! Fiz 2 coleções e mais algumas festas. Até o dia que um menino deu PT de tanto beber e decidi que era hora de tentar outra coisa.
Como assim a Apple não vai vender mais os carregadores?
Isso, foi durante a pandemia. A Apple decidiu vender o telefone e o cabo. E, você que lute com a fonte. Estava difícil achar dinheiro no mercado naqueles tempos e eu pensei. Vou pesquisar no google trends e validar a ideia. Caixa! Tinha mais de 80 pts de busca. Colei em SP, no Brás e comprei literalmente. Todo meu dinheiro de cabo de iphone, carregador e bateria portátil.
Fiquei com R$100 na conta. Para fazer um lanche e pagar pelo uber para voltar para casa. Chegando aqui, eu tirei foto e fiz várias copys. Anunciei no Olx, Mercado Livre e Facebook. Impulsionei os anúncios no OLX, vendi para familiares e amigos, e; vendia até para quem estava na rua. Fiz entrega de bike, a pé, de ônibus e é isso mesmo. Tem que ralar. Para queimar o resto da mercadoria. Deixei com uma loja de eletrônicos e fiz consignado. E, hora da próxima ideia.
Mulheres, doces e TPM
Meu penúltimo negócio veio depois dos cabos. Eu pesquisei na net, negócios online para começar com pouca grana. (Depois que paguei as contas do dia a dia, sobraram R$3mil). E, achei uma pesquisa mostrando que doces. Tinha baixa barreira de entrada e exigia poucos equipamentos. Eu trabalhei em restaurante por muitos anos e sabia como lucrar com aquilo. Além do mais, mulheres consomem mais doce em uma certa época do mês.
Não deu outra, convidei 2 pessoas para serem sócias. Desenvolvemos os produtos, fotografamos e fizemos as copys. Em sequência, precisávamos vender. Então, lá vamos denovo: Ifood, WPP, 99food (na época), Uber eats (na época), Elo7, famílias e amigos e; por fim começamos a vender consignado com alguns restaurantes e lojas. Foi uma época em que aprendi a prospectar clientes de todas as maneiras possíveis.
De novo, minha maior dificuldade era a locomoção para fazer entregas. Só tinha uma bike. Mas, entregávamos. Os primeiros 3 meses foram difíceis demais. Mas, rolou. No fim, nossas maiores vendas vinham de: Ifood, encomendas de festas e consignados. Mas, como nem tudo são flores. Meus dois sócios tomaram outros caminhos e abandonaram o projeto. Galera, está tudo bem com isso. Isso acontece o tempo todo. A vida muda e temos que aprender a aceitar isso. Vida que segue e fui para frente de novo.
Sobre paixões, paciência e acreditar
Estava eu comemorando meu níver de 30 anos, num misto de realizações e pouco realizado. Como assim? Sabe quando você faz um monte de coisas, mas ainda assim. Não sente que é aquilo? Pois então…
Eu amo investimentos, livros, escrever e sempre curti trocar ideia com amigos e família sobre como se desenvolver. Desde que comecei a usar a internet eu criei: Canal no youtube, páginas no IG e FB, pinterest, steemit, blog e até canal no Telegram. Mas, nunca tinha consistente sabe? Tipo assim, vou fazer isso por um ano e plantar 100 sementes aqui. Enfim, inconsistência te derruba meu amigo…Eu voltei a trabalhar com restaurantes e estava doido para mudar de área. Estava exausto de trabalhar e meu wpp não parava de tocar. Fui estudar ADM e Desenvolvimento de sistemas no Senac. Dois anos depois, formei. Consegui trabalho.
E, comecei a pensar em como criar um negócio online, escalável e multilíngue. Passei os próximos 7 meses desenhando e pensando como. Mas, tinha que dar o primeiro passo. Criei um site e fui escrevendo textos. Os primeiros 30 foram aquilo, os próximos 10 melhoraram muito e os 10 a seguir eu fiquei bem satisfeitos. Hoje, tenho o negócio que estava na cabeça desde 2023. Mas, olha o tamanho da volta que o universo me fez dar e aprender para chegar aqui hoje. Dicas? Só 3:
- Você precisa usar a internet para fazer negócio. Em todos os negócios que falei, sempre teve algo online. Não negligencie isso.
- Tem que aprender a vender e se vender.
- Confia em si mesmo e faz sem medo de errar. Porque, advinha? Você vai errar! Mas, vai aprender e melhorar. Tem que persistir…
Por hoje é isso. Tamo junto!
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ bf47c19e:c3d2573b
2025-05-23 22:14:37
@ bf47c19e:c3d2573b
2025-05-23 22:14:37Originalni tekst na antenam.net
22.05.2025 / Autor: Ana Nives Radović
Da nema besplatnog ručka sigurno ste čuli svaki put kad bi neko poželio da naglasi da se sve na neki način plaća, iako možda tu cijenu ne primjećujemo odmah. Međutim, kada govorimo o događaju od kojeg je prošlo tačno 15 godina onda o „ručku“ ne govorimo u prenešenom smislu, već o porudžbini pice čija tržišna vrijednost iz godine u godinu dostiže iznos koji je čini najskupljom hranom koja je ikad poručena.
Tog 22. maja 2010. godine čovjek sa Floride pod imenom Laslo Hanjec potrošio je 10.000 bitcoina na dvije velike pice. U to vrijeme, ta količina bitcoina imala je tržišnu vrijednost od oko 41 dolar. Ako uzmemo u obzir da je vrijednost jedne jedinice ove digitalne valute danas nešto više od 111.000 dolara, tih 10.000 bitcoina danas bi značilo vrijednost od 1,11 milijardi dolara.
Nesvakidašnji događaj u digitalnoj i ugostiteljskoj istoriji, nastao zbog znatiželje poručioca koji je želio da se uvjeri da koristeći bitcoin može da plati nešto u stvarnom svijetu, pretvorio se u Bitcoin Pizza Day, kao podsjetnik na trenutak koji je označio prelaz bitcoina iz apstraktnog kriptografskog eksperimenta u nešto što ima stvarnu vrijednost.
Hanjec je bio znatiželjan i pitao se da li se prva, a u to vrijeme i jedina kriptovaluta može iskoristiti za kupovinu nečeg opipljivog. Objavio je ponudu na jednom forumu koja je glasila: 10.000 BTC za dvije pice. Jedan entuzijasta se javio, naručio pice iz restorana Papa John’s i ispisao zanimljivu stranicu istorije digitalne imovine.
Taj inicijalni zabilježeni finansijski dogovor dao je bitcoinu prvu široko prihvaćenu tržišnu vrijednost: 10.000 BTC za 41 dolar, čime je bitcoin napravio svoj prvi korak ka onome što danas mnogi zovu digitalnim zlatom.
Šta je zapravo bitcoin?
Bitcoin je oblik digitalnog novca koji je osmišljen da bude decentralizovan, transparentan i otporan na uticaj centralnih banaka. Kreirao ga je 2009. godine anonimni autor poznat kao Satoši Nakamoto, neposredno nakon globalne finansijske krize 2008. godine. U svojoj suštini, bitcoin je protokol, skup pravila koja sprovodi kompjuterski kod, koji omogućava korisnicima da bez posrednika sigurno razmjenjuju vrijednost putem interneta.
Osnova cijelog sistema je blockchain, distribuisana digitalna knjiga koju održavaju hiljade nezavisnih računara (tzv. čvorova) širom svijeta. Svaka transakcija se bilježi u novi „blok“, koji se potom dodaje u lanac (otud naziv „lanac blokova“, odnosno blockchain). Informacija koja se jednom upiše u blok ne može da se izbriše, niti promijeni, što omogućava više transparentnosti i više povjerenja.
Da bi blockchain mreža u kojoj se sve to odvija zadržala to svojstvo, bitcoin koristi mehanizam konsenzusa nazvan dokaz rada (proof-of-work), što znači da specijalizovani računari koji „rudare“ bitcoin rješavaju kompleksne matematičke probleme kako bi omogućili obavljanje transakcija i pouzdanost mreže.
Deflatorna priroda bitcoina
Najjednostavniji način da se razumije deflatorna priroda bitcoina je da pogledamo cijene izražene u valuti kojoj plaćamo. Sigurno ste u posljednje vrijeme uhvatili sebe da komentarišete da ono što je prije nekoliko godina koštalo 10 eura danas košta 15 ili više. Budući da to ne zapažate kada je u pitanju cijena samo određenog proizvoda ili usluge, već kao sveprisutan trend, shvatate da se radi o tome da je novac izgubio vrijednost. Na primjer, kada je riječ o euru, otkako je Evropska centralna banka počela intenzivno da doštampava novac svake godine, pa je od 2009. kada je program tzv. „kvantitativnog popuštanja“ započet euro zabilježio kumulativnu inflaciju od 42,09% zbog povećane količine sredstava u opticaju.
Međutim, kada je riječ o bitcoinu, njega nikada neće biti više od 21 milion koliko je izdato prvog dana, a to nepromjenjivo pravilo zapisano je i u njegovom kodu. Ova ograničena ponuda oštro se suprotstavlja principima koji važe kod monetarnih institucija, poput centralnih banaka, koje doštampavaju novac, često da bi povećale količinu u opticaju i tako podstakle finansijske tokove, iako novac zbog toga gubi vrijednost. Nasuprot tome, bitcoin se zadržava na iznosu od 21 milion, pa je upravo ta konačnost osnova za njegovu deflatornu prirodu i mogućnost da vremenom dobija na vrijednosti.
Naravno, ovo ne znači da je cijena bitcoina predodređena da samo raste. Ona je zapravo prilično volatilna i oscilacije su česte, posebno ukoliko, na primjer, posmatramo odnos cijena unutar jedne godine ili nekoliko mjeseci, međutim, gledano sa vremenske distance od četiri do pet godina bilo koji uporedni period od nastanka bitcoina do danas upućuje na to da je cijena u međuvremenu porasla. Taj trend će se nastaviti, tako da, kao ni kada je riječ o drugim sredstvima, poput zlata ili nafte, nema mjesta konstatacijama da je „vrijeme niskih cijena prošlo“.
Šta zapravo znači ovaj dan?
Bitcoin Pizza Day je za mnoge prilika da saznaju ponešto novo o bitcoinu, jer tada imaju priliku da o njemu čuju detalje sa raznih strana, jer kako se ovaj događaj popularizuje stvaraju se i nove prilike za učenje. Takođe, ovaj dan od 2021. obilježavaju picerije širom svijeta, u više od 400 gradova iz najmanje 75 zemalja, jer je za mnoge ovo prilika da korisnike bitcoina navedu da potroše djelić svoje imovine na nešto iz njihove ponude. Naravno, taj iznos je danasd zanemarljivo mali, a cijena jedne pice danas je otprilike 0,00021 bitcoina.
No, dok picerije širom svijeta danas na zabavan način pokušavaju da dođu do novih gostiju, ovaj dan je za mnoge vlasnike bitcoina nešto poput opomene da svoje digitalne novčiće ipak ne treba trošiti na nešto potrošno, jer je budućnost nepredvidiva. Bitcoin Pizza Day je dan kada se ideja pretvorila u valutu, kada su linije koda postale sredstvo razmjene.
Prvi let avionom trajao je svega 12 sekundi, a u poređenju sa današnjim transkontinentalnim linijama to djeluje gotovo neuporedivo i čudno, međutim, od nečega je moralo početi. Porudžbina pice plaćene bitcoinom označile su početak razmjene ove vrste, dok se, na primjer, tokom jučerašnjeg dana obim plaćanja bitcoinom premašio 23 milijarde dolara. Nauka i tehnologija nas podsjećaju na to da sve počinje malim, zanemarivim koracima.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:53:16
@ 6d5c826a:4b27b659
2025-05-23 21:53:16- DefGuard - True enterprise WireGuard with MFA/2FA and SSO. (Source Code)
Apache-2.0Rust - Dockovpn - Out-of-the-box stateless dockerized OpenVPN server which starts in less than 2 seconds. (Source Code)
GPL-2.0Docker - Firezone - WireGuard based VPN Server and Firewall. (Source Code)
Apache-2.0Docker - Gluetun VPN client - VPN client in a thin Docker container for multiple VPN providers, written in Go, and using OpenVPN or Wireguard, DNS over TLS, with a few proxy servers built-in.
MITdocker - Headscale - Self-hostable fork of Tailscale, cross-platform clients, simple to use, built-in (currently experimental) monitoring tools.
BSD-3-ClauseGo - Nebula - A scalable p2p VPN with a focus on performance, simplicity and security.
MITGo - ocserv - Cisco AnyConnect-compatible VPN server. (Source Code)
GPL-2.0C - OpenVPN - Uses a custom security protocol that utilizes SSL/TLS for key exchange. (Source Code)
GPL-2.0C - SoftEther - Multi-protocol software VPN with advanced features. (Source Code)
Apache-2.0C - sshuttle - Poor man's VPN.
LGPL-2.1Python - strongSwan - Complete IPsec implementation for Linux. (Source Code)
GPL-2.0C - WireGuard - Very fast VPN based on elliptic curve and public key crypto. (Source Code)
GPL-2.0C
- DefGuard - True enterprise WireGuard with MFA/2FA and SSO. (Source Code)
-
 @ c066aac5:6a41a034
2025-04-27 00:35:38
@ c066aac5:6a41a034
2025-04-27 00:35:38I work in the business world as a salesperson. I am frequently out and about in the community trying to make friends, connect with people who I can help, and ultimately grow my book of business. I have goals set by my employers and I aim to meet those expectations. Because of this, I find myself frequently under pressure to find ways to produce. This often leads to me being disappointed in myself; my sales cycles are long and I lose more deals than I win. My Dad often reminds me that How to Win Friends and Influence People has all the secrets of sales I'll ever need, but I still end up wishing I could find that secret edge to out-do the competition. That's where the watch temptation comes in.
I frequently see a luxurious timepiece on the left wrist of my peers and elder-statesmen closers. Rolex, Omega, Patek, a whole world of $10k minimum machines. It comes across as a power-move, a symbol of status that is hard to ignore. It sends a message that the bearer's time is more valuable than that of other people. It makes me think "if this person is wearing that watch, that means they're great at what they do." The ultimate investment in one's self.
As a newly married man expecting a child, it is hard for me to stomach such a purchase. My wife has supported the idea of me potentially getting such a timepiece; as much as it tickles my fancy, I'd rather put my capital towards things that further my family than my clout. One of the things that struck me was a statement made by an investment advisor in my Kiwanis club: "A watch is a purchase, not an investment."
What a true statement! His words helped me escape my short-lived delusions. That said, I still look at watches sometimes on the internet (The Omega No Time to Die watch is sleek looking). One day, I found myself looking at houses online shortly after looking at watches online. Then it hit me: how many purchases are being marketed as investments in this era? A Rolex is a supposed investment in your career, not just a luxury timepiece. A house is a mechanism for monetary growth, not an attainable home to be enjoyed by a family. A college degree is an investment for your future, not a vehicle for building upon passions.
The Bitcoiners will repeat the phrase "fix the money, fix the world" in harmonious chorus to address the concern I have laid out in this article. Ultimately, I leave you with this reminder: don't let the world pass off things that should be inconsequential purchases as investments with ROIs. I believe the only true investment one can make is into the people around them; that will yield the greatest rewards for the soul.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:52:59
@ 6d5c826a:4b27b659
2025-05-23 21:52:59- Ganeti - Cluster virtual server management software tool built on top of KVM and Xen. (Source Code)
BSD-2-ClausePython/Haskell - KVM - Linux kernel virtualization infrastructure. (Source Code)
GPL-2.0/LGPL-2.0C - OpenNebula - Build and manage enterprise clouds for virtualized services, containerized applications and serverless computing. (Source Code)
Apache-2.0C++ - oVirt - Manages virtual machines, storage and virtual networks. (Source Code)
Apache-2.0Java - Packer - A tool for creating identical machine images for multiple platforms from a single source configuration. (Source Code)
MPL-2.0Go - Proxmox VE - Virtualization management solution. (Source Code)
GPL-2.0Perl/Shell - QEMU - QEMU is a generic machine emulator and virtualizer. (Source Code)
LGPL-2.1C - Vagrant - Tool for building complete development environments. (Source Code)
BUSL-1.1Ruby - VirtualBox - Virtualization product from Oracle Corporation. (Source Code)
GPL-3.0/CDDL-1.0C++ - XCP-ng - Virtualization platform based on Xen Source and Citrix® Hypervisor (formerly XenServer). (Source Code)
GPL-2.0C - Xen - Virtual machine monitor for 32/64 bit Intel / AMD (IA 64) and PowerPC 970 architectures. (Source Code)
GPL-2.0C
- Ganeti - Cluster virtual server management software tool built on top of KVM and Xen. (Source Code)
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:52:43
@ 6d5c826a:4b27b659
2025-05-23 21:52:43- Darcs - Cross-platform version control system, like git, mercurial or svn but with a very different approach: focus on changes rather than snapshots. (Source Code)
GPL-2.0Haskell - Fossil - Distributed version control with built-in wiki and bug tracking. (Source Code)
BSD-2-ClauseC - Git - Distributed revision control and source code management (SCM) with an emphasis on speed. (Source Code)
GPL-2.0C - Mercurial - Distributed source control management tool. (Source Code)
GPL-2.0Python/C/Rust - Subversion - Client-server revision control system. (Source Code)
Apache-2.0C
- Darcs - Cross-platform version control system, like git, mercurial or svn but with a very different approach: focus on changes rather than snapshots. (Source Code)
-
 @ 24462930:3caf03ab
2025-04-25 04:37:25
@ 24462930:3caf03ab
2025-04-25 04:37:25Nostr 中所有的数据都是事件,通过将事件存储在多个中继器上来实现去中心化,通过签名来证明事件的拥有者。但如果你想真正拥有你的事件,你应该运行一个自己的中继器来保存它们。否则一旦你使用的所有中继器出了故障或者刻意删除了你的事件,你将永远丢失它们。
对于大部份人来说,运行一个中继器是复杂的,成本高昂的。为了解决这个问题,我开发了 nostr-relay-tray,这是一款可以很方便在个人电脑上运行的中继器,并且支持通过互联网对其进行访问。
项目地址:https://github.com/CodyTseng/nostr-relay-tray
本文将介绍如何使用 nostr-relay-tray 来运行一个自己的中继器。
下载
从 GitHub Release 页面 下载对应你操作系统的安装包
| 操作系统 | 文件格式 | | --------------------- | ---------------------------------- | | Windows |
nostr-relay-tray.Setup.x.x.x.exe| | macOS (Apple Silicon) |nostr-relay-tray-x.x.x-arm64.dmg| | macOS (Intel) |nostr-relay-tray-x.x.x.dmg| | Linux | 你们应该知道使用哪个 |安装
因为我没有对这个安装包进行数字签名,所以在安装时会有一些阻碍。安装成功后,菜单栏会出现一个鸵鸟图标。点击鸵鸟图标,你会看到一个菜单,点击 "Dashboard" 选项可以打开中继器的控制面板进行更多的配置。

macOS 用户注意:
- 首次打开时需要前往「系统设置 > 隐私与安全性」点击“仍要打开”按钮。
- 若遇损坏提示,需要在终端执行以下命令解除限制:
bash sudo xattr -rd com.apple.quarantine /Applications/nostr-relay-tray.appWindows 用户:
- 在安全警告界面点击「更多信息 > 仍要运行」
连接
默认情况下,nostr-relay-tray 只能在本地通过
ws://localhost:4869/进行访问。这让它的用途非常有限,所以我们需要将它暴露到互联网。在控制面板中点击 "Proxy" 选项卡,并打开开关。你将会获得一个 "Public address",你可以使用这个地址在任何地方访问你的中继器。就是这么简单。
接下来,你要将刚刚获得的地址添加到你的中继器列表中。并且要让它在列表中尽可能靠前的位置。因为大部份的客户端会优先连接列表中靠前的中继器,后面的中继器常常会被忽略。

限制
接下来我们需要增加一些限制来防止中继器保存一些与你无关的事件,浪费存储空间。nostr-relay-tray 可以非常灵活精细地设置允许接收哪些事件,但有些复杂,所以不在这里介绍,如果有兴趣可以日后探索。
在这里我先介绍一个很简单有效的策略 —— WoT (Web of Trust)。你可以在 "WoT & PoW" 选项卡中打开这个功能。打开之前你需要先输入你的 pubkey。
这里还有一个非常重要的参数
Depth,它表示某个人与你的关系深度。你关注的人与你的深度为 1,你关注的人关注的人与你的深度为 2,以此类推。- 如果你将这个参数设置为 0,那么你的中继器只会接收你自己的事件。
- 如果你将这个参数设置为 1,那么你的中继器只会接收你和你关注的人的事件。
- 如果你将这个参数设置为 2,那么你的中继器只会接收你和你关注的人的事件,以及你关注的人关注的人的事件。
目前这个参数的最大值只能为 2。

总结
至此,你已经成功运行了一个自己的中继器,并且设置了一个简单的限制来防止中继器保存一些与你无关的事件。
如果你在使用中遇到任何问题,请随时在 GitHub 上提交 issue,我会尽快回复你。
Not your relay, not your events
-
 @ 40b9c85f:5e61b451
2025-04-24 15:27:02
@ 40b9c85f:5e61b451
2025-04-24 15:27:02Introduction
Data Vending Machines (DVMs) have emerged as a crucial component of the Nostr ecosystem, offering specialized computational services to clients across the network. As defined in NIP-90, DVMs operate on an apparently simple principle: "data in, data out." They provide a marketplace for data processing where users request specific jobs (like text translation, content recommendation, or AI text generation)
While DVMs have gained significant traction, the current specification faces challenges that hinder widespread adoption and consistent implementation. This article explores some ideas on how we can apply the reflection pattern, a well established approach in RPC systems, to address these challenges and improve the DVM ecosystem's clarity, consistency, and usability.
The Current State of DVMs: Challenges and Limitations
The NIP-90 specification provides a broad framework for DVMs, but this flexibility has led to several issues:
1. Inconsistent Implementation
As noted by hzrd149 in "DVMs were a mistake" every DVM implementation tends to expect inputs in slightly different formats, even while ostensibly following the same specification. For example, a translation request DVM might expect an event ID in one particular format, while an LLM service could expect a "prompt" input that's not even specified in NIP-90.
2. Fragmented Specifications
The DVM specification reserves a range of event kinds (5000-6000), each meant for different types of computational jobs. While creating sub-specifications for each job type is being explored as a possible solution for clarity, in a decentralized and permissionless landscape like Nostr, relying solely on specification enforcement won't be effective for creating a healthy ecosystem. A more comprehensible approach is needed that works with, rather than against, the open nature of the protocol.
3. Ambiguous API Interfaces
There's no standardized way for clients to discover what parameters a specific DVM accepts, which are required versus optional, or what output format to expect. This creates uncertainty and forces developers to rely on documentation outside the protocol itself, if such documentation exists at all.
The Reflection Pattern: A Solution from RPC Systems
The reflection pattern in RPC systems offers a compelling solution to many of these challenges. At its core, reflection enables servers to provide metadata about their available services, methods, and data types at runtime, allowing clients to dynamically discover and interact with the server's API.
In established RPC frameworks like gRPC, reflection serves as a self-describing mechanism where services expose their interface definitions and requirements. In MCP reflection is used to expose the capabilities of the server, such as tools, resources, and prompts. Clients can learn about available capabilities without prior knowledge, and systems can adapt to changes without requiring rebuilds or redeployments. This standardized introspection creates a unified way to query service metadata, making tools like
grpcurlpossible without requiring precompiled stubs.How Reflection Could Transform the DVM Specification
By incorporating reflection principles into the DVM specification, we could create a more coherent and predictable ecosystem. DVMs already implement some sort of reflection through the use of 'nip90params', which allow clients to discover some parameters, constraints, and features of the DVMs, such as whether they accept encryption, nutzaps, etc. However, this approach could be expanded to provide more comprehensive self-description capabilities.
1. Defined Lifecycle Phases
Similar to the Model Context Protocol (MCP), DVMs could benefit from a clear lifecycle consisting of an initialization phase and an operation phase. During initialization, the client and DVM would negotiate capabilities and exchange metadata, with the DVM providing a JSON schema containing its input requirements. nip-89 (or other) announcements can be used to bootstrap the discovery and negotiation process by providing the input schema directly. Then, during the operation phase, the client would interact with the DVM according to the negotiated schema and parameters.
2. Schema-Based Interactions
Rather than relying on rigid specifications for each job type, DVMs could self-advertise their schemas. This would allow clients to understand which parameters are required versus optional, what type validation should occur for inputs, what output formats to expect, and what payment flows are supported. By internalizing the input schema of the DVMs they wish to consume, clients gain clarity on how to interact effectively.
3. Capability Negotiation
Capability negotiation would enable DVMs to advertise their supported features, such as encryption methods, payment options, or specialized functionalities. This would allow clients to adjust their interaction approach based on the specific capabilities of each DVM they encounter.
Implementation Approach
While building DVMCP, I realized that the RPC reflection pattern used there could be beneficial for constructing DVMs in general. Since DVMs already follow an RPC style for their operation, and reflection is a natural extension of this approach, it could significantly enhance and clarify the DVM specification.
A reflection enhanced DVM protocol could work as follows: 1. Discovery: Clients discover DVMs through existing NIP-89 application handlers, input schemas could also be advertised in nip-89 announcements, making the second step unnecessary. 2. Schema Request: Clients request the DVM's input schema for the specific job type they're interested in 3. Validation: Clients validate their request against the provided schema before submission 4. Operation: The job proceeds through the standard NIP-90 flow, but with clearer expectations on both sides
Parallels with Other Protocols
This approach has proven successful in other contexts. The Model Context Protocol (MCP) implements a similar lifecycle with capability negotiation during initialization, allowing any client to communicate with any server as long as they adhere to the base protocol. MCP and DVM protocols share fundamental similarities, both aim to expose and consume computational resources through a JSON-RPC-like interface, albeit with specific differences.
gRPC's reflection service similarly allows clients to discover service definitions at runtime, enabling generic tools to work with any gRPC service without prior knowledge. In the REST API world, OpenAPI/Swagger specifications document interfaces in a way that makes them discoverable and testable.
DVMs would benefit from adopting these patterns while maintaining the decentralized, permissionless nature of Nostr.
Conclusion
I am not attempting to rewrite the DVM specification; rather, explore some ideas that could help the ecosystem improve incrementally, reducing fragmentation and making the ecosystem more comprehensible. By allowing DVMs to self describe their interfaces, we could maintain the flexibility that makes Nostr powerful while providing the structure needed for interoperability.
For developers building DVM clients or libraries, this approach would simplify consumption by providing clear expectations about inputs and outputs. For DVM operators, it would establish a standard way to communicate their service's requirements without relying on external documentation.
I am currently developing DVMCP following these patterns. Of course, DVMs and MCP servers have different details; MCP includes capabilities such as tools, resources, and prompts on the server side, as well as 'roots' and 'sampling' on the client side, creating a bidirectional way to consume capabilities. In contrast, DVMs typically function similarly to MCP tools, where you call a DVM with an input and receive an output, with each job type representing a different categorization of the work performed.
Without further ado, I hope this article has provided some insight into the potential benefits of applying the reflection pattern to the DVM specification.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:52:26
@ 6d5c826a:4b27b659
2025-05-23 21:52:26- grml - Bootable Debian Live CD with powerful CLI tools. (Source Code)
GPL-3.0Shell - mitmproxy - A Python tool used for intercepting, viewing and modifying network traffic. Invaluable in troubleshooting certain problems. (Source Code)
MITPython - mtr - Network utility that combines traceroute and ping. (Source Code)
GPL-2.0C - Sysdig - Capture system state and activity from a running Linux instance, then save, filter and analyze. (Source Code)
Apache-2.0Docker/Lua/C - Wireshark - The world's foremost network protocol analyzer. (Source Code)
GPL-2.0C
- grml - Bootable Debian Live CD with powerful CLI tools. (Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:52:06
@ 6d5c826a:4b27b659
2025-05-23 21:52:06- Docker Compose - Define and run multi-container Docker applications. (Source Code)
Apache-2.0Go - Docker Swarm - Manage cluster of Docker Engines. (Source Code)
Apache-2.0Go - Docker - Platform for developers and sysadmins to build, ship, and run distributed applications. (Source Code)
Apache-2.0Go - LXC - Userspace interface for the Linux kernel containment features. (Source Code)
GPL-2.0C - LXD - Container "hypervisor" and a better UX for LXC. (Source Code)
Apache-2.0Go - OpenVZ - Container-based virtualization for Linux. (Source Code)
GPL-2.0C - Podman - Daemonless container engine for developing, managing, and running OCI Containers on your Linux System. Containers can either be run as root or in rootless mode. Simply put:
alias docker=podman. (Source Code)Apache-2.0Go - Portainer Community Edition - Simple management UI for Docker. (Source Code)
ZlibGo - systemd-nspawn - Lightweight, chroot-like, environment to run an OS or command directly under systemd. (Source Code)
GPL-2.0C
- Docker Compose - Define and run multi-container Docker applications. (Source Code)
-
 @ a39d19ec:3d88f61e
2025-04-22 12:44:42
@ a39d19ec:3d88f61e
2025-04-22 12:44:42Die Debatte um Migration, Grenzsicherung und Abschiebungen wird in Deutschland meist emotional geführt. Wer fordert, dass illegale Einwanderer abgeschoben werden, sieht sich nicht selten dem Vorwurf des Rassismus ausgesetzt. Doch dieser Vorwurf ist nicht nur sachlich unbegründet, sondern verkehrt die Realität ins Gegenteil: Tatsächlich sind es gerade diejenigen, die hinter jeder Forderung nach Rechtssicherheit eine rassistische Motivation vermuten, die selbst in erster Linie nach Hautfarbe, Herkunft oder Nationalität urteilen.
Das Recht steht über Emotionen
Deutschland ist ein Rechtsstaat. Das bedeutet, dass Regeln nicht nach Bauchgefühl oder politischer Stimmungslage ausgelegt werden können, sondern auf klaren gesetzlichen Grundlagen beruhen müssen. Einer dieser Grundsätze ist in Artikel 16a des Grundgesetzes verankert. Dort heißt es:
„Auf Absatz 1 [Asylrecht] kann sich nicht berufen, wer aus einem Mitgliedstaat der Europäischen Gemeinschaften oder aus einem anderen Drittstaat einreist, in dem die Anwendung des Abkommens über die Rechtsstellung der Flüchtlinge und der Europäischen Menschenrechtskonvention sichergestellt ist.“
Das bedeutet, dass jeder, der über sichere Drittstaaten nach Deutschland einreist, keinen Anspruch auf Asyl hat. Wer dennoch bleibt, hält sich illegal im Land auf und unterliegt den geltenden Regelungen zur Rückführung. Die Forderung nach Abschiebungen ist daher nichts anderes als die Forderung nach der Einhaltung von Recht und Gesetz.
Die Umkehrung des Rassismusbegriffs
Wer einerseits behauptet, dass das deutsche Asyl- und Aufenthaltsrecht strikt durchgesetzt werden soll, und andererseits nicht nach Herkunft oder Hautfarbe unterscheidet, handelt wertneutral. Diejenigen jedoch, die in einer solchen Forderung nach Rechtsstaatlichkeit einen rassistischen Unterton sehen, projizieren ihre eigenen Denkmuster auf andere: Sie unterstellen, dass die Debatte ausschließlich entlang ethnischer, rassistischer oder nationaler Kriterien geführt wird – und genau das ist eine rassistische Denkweise.
Jemand, der illegale Einwanderung kritisiert, tut dies nicht, weil ihn die Herkunft der Menschen interessiert, sondern weil er den Rechtsstaat respektiert. Hingegen erkennt jemand, der hinter dieser Kritik Rassismus wittert, offenbar in erster Linie die „Rasse“ oder Herkunft der betreffenden Personen und reduziert sie darauf.
Finanzielle Belastung statt ideologischer Debatte
Neben der rechtlichen gibt es auch eine ökonomische Komponente. Der deutsche Wohlfahrtsstaat basiert auf einem Solidarprinzip: Die Bürger zahlen in das System ein, um sich gegenseitig in schwierigen Zeiten zu unterstützen. Dieser Wohlstand wurde über Generationen hinweg von denjenigen erarbeitet, die hier seit langem leben. Die Priorität liegt daher darauf, die vorhandenen Mittel zuerst unter denjenigen zu verteilen, die durch Steuern, Sozialabgaben und Arbeit zum Erhalt dieses Systems beitragen – nicht unter denen, die sich durch illegale Einreise und fehlende wirtschaftliche Eigenleistung in das System begeben.
Das ist keine ideologische Frage, sondern eine rein wirtschaftliche Abwägung. Ein Sozialsystem kann nur dann nachhaltig funktionieren, wenn es nicht unbegrenzt belastet wird. Würde Deutschland keine klaren Regeln zur Einwanderung und Abschiebung haben, würde dies unweigerlich zur Überlastung des Sozialstaates führen – mit negativen Konsequenzen für alle.
Sozialpatriotismus
Ein weiterer wichtiger Aspekt ist der Schutz der Arbeitsleistung jener Generationen, die Deutschland nach dem Zweiten Weltkrieg mühsam wieder aufgebaut haben. Während oft betont wird, dass die Deutschen moralisch kein Erbe aus der Zeit vor 1945 beanspruchen dürfen – außer der Verantwortung für den Holocaust –, ist es umso bedeutsamer, das neue Erbe nach 1945 zu respektieren, das auf Fleiß, Disziplin und harter Arbeit beruht. Der Wiederaufbau war eine kollektive Leistung deutscher Menschen, deren Früchte nicht bedenkenlos verteilt werden dürfen, sondern vorrangig denjenigen zugutekommen sollten, die dieses Fundament mitgeschaffen oder es über Generationen mitgetragen haben.
Rechtstaatlichkeit ist nicht verhandelbar
Wer sich für eine konsequente Abschiebepraxis ausspricht, tut dies nicht aus rassistischen Motiven, sondern aus Respekt vor der Rechtsstaatlichkeit und den wirtschaftlichen Grundlagen des Landes. Der Vorwurf des Rassismus in diesem Kontext ist daher nicht nur falsch, sondern entlarvt eine selektive Wahrnehmung nach rassistischen Merkmalen bei denjenigen, die ihn erheben.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:49:50
@ 6d5c826a:4b27b659
2025-05-23 21:49:50- Consul - Consul is a tool for service discovery, monitoring and configuration. (Source Code)
MPL-2.0Go - etcd - Distributed K/V-Store, authenticating via SSL PKI and a REST HTTP Api for shared configuration and service discovery. (Source Code)
Apache-2.0Go - ZooKeeper - ZooKeeper is a centralized service for maintaining configuration information, naming, providing distributed synchronization, and providing group services. (Source Code)
Apache-2.0Java/C++
- Consul - Consul is a tool for service discovery, monitoring and configuration. (Source Code)
-
 @ 4ba8e86d:89d32de4
2025-04-21 02:13:56
@ 4ba8e86d:89d32de4
2025-04-21 02:13:56Tutorial feito por nostr:nostr:npub1rc56x0ek0dd303eph523g3chm0wmrs5wdk6vs0ehd0m5fn8t7y4sqra3tk poste original abaixo:
Parte 1 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/263585/tutorial-debloat-de-celulares-android-via-adb-parte-1
Parte 2 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/index.php/263586/tutorial-debloat-de-celulares-android-via-adb-parte-2
Quando o assunto é privacidade em celulares, uma das medidas comumente mencionadas é a remoção de bloatwares do dispositivo, também chamado de debloat. O meio mais eficiente para isso sem dúvidas é a troca de sistema operacional. Custom Rom’s como LineageOS, GrapheneOS, Iodé, CalyxOS, etc, já são bastante enxutos nesse quesito, principalmente quanto não é instalado os G-Apps com o sistema. No entanto, essa prática pode acabar resultando em problemas indesejados como a perca de funções do dispositivo, e até mesmo incompatibilidade com apps bancários, tornando este método mais atrativo para quem possui mais de um dispositivo e separando um apenas para privacidade. Pensando nisso, pessoas que possuem apenas um único dispositivo móvel, que são necessitadas desses apps ou funções, mas, ao mesmo tempo, tem essa visão em prol da privacidade, buscam por um meio-termo entre manter a Stock rom, e não ter seus dados coletados por esses bloatwares. Felizmente, a remoção de bloatwares é possível e pode ser realizada via root, ou mais da maneira que este artigo irá tratar, via adb.
O que são bloatwares?
Bloatware é a junção das palavras bloat (inchar) + software (programa), ou seja, um bloatware é basicamente um programa inútil ou facilmente substituível — colocado em seu dispositivo previamente pela fabricante e operadora — que está no seu dispositivo apenas ocupando espaço de armazenamento, consumindo memória RAM e pior, coletando seus dados e enviando para servidores externos, além de serem mais pontos de vulnerabilidades.
O que é o adb?
O Android Debug Brigde, ou apenas adb, é uma ferramenta que se utiliza das permissões de usuário shell e permite o envio de comandos vindo de um computador para um dispositivo Android exigindo apenas que a depuração USB esteja ativa, mas também pode ser usada diretamente no celular a partir do Android 11, com o uso do Termux e a depuração sem fio (ou depuração wifi). A ferramenta funciona normalmente em dispositivos sem root, e também funciona caso o celular esteja em Recovery Mode.
Requisitos:
Para computadores:
• Depuração USB ativa no celular; • Computador com adb; • Cabo USB;
Para celulares:
• Depuração sem fio (ou depuração wifi) ativa no celular; • Termux; • Android 11 ou superior;
Para ambos:
• Firewall NetGuard instalado e configurado no celular; • Lista de bloatwares para seu dispositivo;
Ativação de depuração:
Para ativar a Depuração USB em seu dispositivo, pesquise como ativar as opções de desenvolvedor de seu dispositivo, e lá ative a depuração. No caso da depuração sem fio, sua ativação irá ser necessária apenas no momento que for conectar o dispositivo ao Termux.
Instalação e configuração do NetGuard
O NetGuard pode ser instalado através da própria Google Play Store, mas de preferência instale pela F-Droid ou Github para evitar telemetria.
F-Droid: https://f-droid.org/packages/eu.faircode.netguard/
Github: https://github.com/M66B/NetGuard/releases
Após instalado, configure da seguinte maneira:
Configurações → padrões (lista branca/negra) → ative as 3 primeiras opções (bloquear wifi, bloquear dados móveis e aplicar regras ‘quando tela estiver ligada’);
Configurações → opções avançadas → ative as duas primeiras (administrar aplicativos do sistema e registrar acesso a internet);
Com isso, todos os apps estarão sendo bloqueados de acessar a internet, seja por wifi ou dados móveis, e na página principal do app basta permitir o acesso a rede para os apps que você vai usar (se necessário). Permita que o app rode em segundo plano sem restrição da otimização de bateria, assim quando o celular ligar, ele já estará ativo.
Lista de bloatwares
Nem todos os bloatwares são genéricos, haverá bloatwares diferentes conforme a marca, modelo, versão do Android, e até mesmo região.
Para obter uma lista de bloatwares de seu dispositivo, caso seu aparelho já possua um tempo de existência, você encontrará listas prontas facilmente apenas pesquisando por elas. Supondo que temos um Samsung Galaxy Note 10 Plus em mãos, basta pesquisar em seu motor de busca por:
Samsung Galaxy Note 10 Plus bloatware listProvavelmente essas listas já terão inclusas todos os bloatwares das mais diversas regiões, lhe poupando o trabalho de buscar por alguma lista mais específica.
Caso seu aparelho seja muito recente, e/ou não encontre uma lista pronta de bloatwares, devo dizer que você acaba de pegar em merda, pois é chato para um caralho pesquisar por cada aplicação para saber sua função, se é essencial para o sistema ou se é facilmente substituível.
De antemão já aviso, que mais para frente, caso vossa gostosura remova um desses aplicativos que era essencial para o sistema sem saber, vai acabar resultando na perda de alguma função importante, ou pior, ao reiniciar o aparelho o sistema pode estar quebrado, lhe obrigando a seguir com uma formatação, e repetir todo o processo novamente.
Download do adb em computadores
Para usar a ferramenta do adb em computadores, basta baixar o pacote chamado SDK platform-tools, disponível através deste link: https://developer.android.com/tools/releases/platform-tools. Por ele, você consegue o download para Windows, Mac e Linux.
Uma vez baixado, basta extrair o arquivo zipado, contendo dentro dele uma pasta chamada platform-tools que basta ser aberta no terminal para se usar o adb.
Download do adb em celulares com Termux.
Para usar a ferramenta do adb diretamente no celular, antes temos que baixar o app Termux, que é um emulador de terminal linux, e já possui o adb em seu repositório. Você encontra o app na Google Play Store, mas novamente recomendo baixar pela F-Droid ou diretamente no Github do projeto.
F-Droid: https://f-droid.org/en/packages/com.termux/
Github: https://github.com/termux/termux-app/releases
Processo de debloat
Antes de iniciarmos, é importante deixar claro que não é para você sair removendo todos os bloatwares de cara sem mais nem menos, afinal alguns deles precisam antes ser substituídos, podem ser essenciais para você para alguma atividade ou função, ou até mesmo são insubstituíveis.
Alguns exemplos de bloatwares que a substituição é necessária antes da remoção, é o Launcher, afinal, é a interface gráfica do sistema, e o teclado, que sem ele só é possível digitar com teclado externo. O Launcher e teclado podem ser substituídos por quaisquer outros, minha recomendação pessoal é por aqueles que respeitam sua privacidade, como Pie Launcher e Simple Laucher, enquanto o teclado pelo OpenBoard e FlorisBoard, todos open-source e disponíveis da F-Droid.
Identifique entre a lista de bloatwares, quais você gosta, precisa ou prefere não substituir, de maneira alguma você é obrigado a remover todos os bloatwares possíveis, modifique seu sistema a seu bel-prazer. O NetGuard lista todos os apps do celular com o nome do pacote, com isso você pode filtrar bem qual deles não remover.
Um exemplo claro de bloatware insubstituível e, portanto, não pode ser removido, é o com.android.mtp, um protocolo onde sua função é auxiliar a comunicação do dispositivo com um computador via USB, mas por algum motivo, tem acesso a rede e se comunica frequentemente com servidores externos. Para esses casos, e melhor solução mesmo é bloquear o acesso a rede desses bloatwares com o NetGuard.
MTP tentando comunicação com servidores externos:
Executando o adb shell
No computador
Faça backup de todos os seus arquivos importantes para algum armazenamento externo, e formate seu celular com o hard reset. Após a formatação, e a ativação da depuração USB, conecte seu aparelho e o pc com o auxílio de um cabo USB. Muito provavelmente seu dispositivo irá apenas começar a carregar, por isso permita a transferência de dados, para que o computador consiga se comunicar normalmente com o celular.
Já no pc, abra a pasta platform-tools dentro do terminal, e execute o seguinte comando:
./adb start-serverO resultado deve ser:
daemon not running; starting now at tcp:5037 daemon started successfully
E caso não apareça nada, execute:
./adb kill-serverE inicie novamente.
Com o adb conectado ao celular, execute:
./adb shellPara poder executar comandos diretamente para o dispositivo. No meu caso, meu celular é um Redmi Note 8 Pro, codinome Begonia.
Logo o resultado deve ser:
begonia:/ $
Caso ocorra algum erro do tipo:
adb: device unauthorized. This adb server’s $ADB_VENDOR_KEYS is not set Try ‘adb kill-server’ if that seems wrong. Otherwise check for a confirmation dialog on your device.
Verifique no celular se apareceu alguma confirmação para autorizar a depuração USB, caso sim, autorize e tente novamente. Caso não apareça nada, execute o kill-server e repita o processo.
No celular
Após realizar o mesmo processo de backup e hard reset citado anteriormente, instale o Termux e, com ele iniciado, execute o comando:
pkg install android-toolsQuando surgir a mensagem “Do you want to continue? [Y/n]”, basta dar enter novamente que já aceita e finaliza a instalação
Agora, vá até as opções de desenvolvedor, e ative a depuração sem fio. Dentro das opções da depuração sem fio, terá uma opção de emparelhamento do dispositivo com um código, que irá informar para você um código em emparelhamento, com um endereço IP e porta, que será usado para a conexão com o Termux.
Para facilitar o processo, recomendo que abra tanto as configurações quanto o Termux ao mesmo tempo, e divida a tela com os dois app’s, como da maneira a seguir:
Para parear o Termux com o dispositivo, não é necessário digitar o ip informado, basta trocar por “localhost”, já a porta e o código de emparelhamento, deve ser digitado exatamente como informado. Execute:
adb pair localhost:porta CódigoDeEmparelhamentoDe acordo com a imagem mostrada anteriormente, o comando ficaria “adb pair localhost:41255 757495”.
Com o dispositivo emparelhado com o Termux, agora basta conectar para conseguir executar os comandos, para isso execute:
adb connect localhost:portaObs: a porta que você deve informar neste comando não é a mesma informada com o código de emparelhamento, e sim a informada na tela principal da depuração sem fio.
Pronto! Termux e adb conectado com sucesso ao dispositivo, agora basta executar normalmente o adb shell:
adb shellRemoção na prática Com o adb shell executado, você está pronto para remover os bloatwares. No meu caso, irei mostrar apenas a remoção de um app (Google Maps), já que o comando é o mesmo para qualquer outro, mudando apenas o nome do pacote.
Dentro do NetGuard, verificando as informações do Google Maps:
Podemos ver que mesmo fora de uso, e com a localização do dispositivo desativado, o app está tentando loucamente se comunicar com servidores externos, e informar sabe-se lá que peste. Mas sem novidades até aqui, o mais importante é que podemos ver que o nome do pacote do Google Maps é com.google.android.apps.maps, e para o remover do celular, basta executar:
pm uninstall –user 0 com.google.android.apps.mapsE pronto, bloatware removido! Agora basta repetir o processo para o resto dos bloatwares, trocando apenas o nome do pacote.
Para acelerar o processo, você pode já criar uma lista do bloco de notas com os comandos, e quando colar no terminal, irá executar um atrás do outro.
Exemplo de lista:
Caso a donzela tenha removido alguma coisa sem querer, também é possível recuperar o pacote com o comando:
cmd package install-existing nome.do.pacotePós-debloat
Após limpar o máximo possível o seu sistema, reinicie o aparelho, caso entre no como recovery e não seja possível dar reboot, significa que você removeu algum app “essencial” para o sistema, e terá que formatar o aparelho e repetir toda a remoção novamente, desta vez removendo poucos bloatwares de uma vez, e reiniciando o aparelho até descobrir qual deles não pode ser removido. Sim, dá trabalho… quem mandou querer privacidade?
Caso o aparelho reinicie normalmente após a remoção, parabéns, agora basta usar seu celular como bem entender! Mantenha o NetGuard sempre executando e os bloatwares que não foram possíveis remover não irão se comunicar com servidores externos, passe a usar apps open source da F-Droid e instale outros apps através da Aurora Store ao invés da Google Play Store.
Referências: Caso você seja um Australopithecus e tenha achado este guia difícil, eis uma videoaula (3:14:40) do Anderson do canal Ciberdef, realizando todo o processo: http://odysee.com/@zai:5/Como-remover-at%C3%A9-200-APLICATIVOS-que-colocam-a-sua-PRIVACIDADE-E-SEGURAN%C3%87A-em-risco.:4?lid=6d50f40314eee7e2f218536d9e5d300290931d23
Pdf’s do Anderson citados na videoaula: créditos ao anon6837264 http://eternalcbrzpicytj4zyguygpmkjlkddxob7tptlr25cdipe5svyqoqd.onion/file/3863a834d29285d397b73a4af6fb1bbe67c888d72d30/t-05e63192d02ffd.pdf
Processo de instalação do Termux e adb no celular: https://youtu.be/APolZrPHSms
-
 @ 6d5c826a:4b27b659
2025-05-23 21:49:30
@ 6d5c826a:4b27b659
2025-05-23 21:49:30- DD-WRT - A Linux-based firmware for wireless routers and access points, originally designed for the Linksys WRT54G series. (Source Code)
GPL-2.0C - OpenWrt - A Linux-based router featuring Mesh networking, IPS via snort and AQM among many other features. (Source Code)
GPL-2.0C - OPNsense - An open source FreeBSD-based firewall and router with traffic shaping, load balancing, and virtual private network capabilities. (Source Code)
BSD-2-ClauseC/PHP - pfSense CE - Free network firewall distribution, based on the FreeBSD operating system with a custom kernel and including third party free software packages for additional functionality. (Source Code)
Apache-2.0Shell/PHP/Other
- DD-WRT - A Linux-based firmware for wireless routers and access points, originally designed for the Linksys WRT54G series. (Source Code)
-
 @ f7d424b5:618c51e8
2025-04-19 22:06:47
@ f7d424b5:618c51e8
2025-04-19 22:06:47It's our podcast and we'll talk about whatever we want. Welcome to a return to normalcy where we cover a variety of subjects instead of just a couple of really long ones. Crack open a beer and chill with us. We're gonna talk about the Galaxy showcase, Marathon, Skyblivion & the leaked Oblivion remake, and a whole bunch more.
In the opening of the episode we get Vic's reaction to a really specific trailer, if you want to follow along, this is the link to that video
Other stuff cited:
Obligatory:
- Listen to the new episode here!
- Discuss this episode on OUR NEW FORUM
- Get the RSS and Subscribe (this is a new feed URL, but the old one redirects here too!)
- Get a modern podcast app to use that RSS feed on at newpodcastapps.com
- Or listen to the show on the forum using the embedded Podverse player!
- Send your complaints here
Reminder that this is a Value4Value podcast so any support you can give us via a modern podcasting app is greatly appreciated and we will never bow to corporate sponsors!
-
 @ 6d5c826a:4b27b659
2025-05-23 21:49:12
@ 6d5c826a:4b27b659
2025-05-23 21:49:12- Remmina - Feature-rich remote desktop application for linux and other unixes. (Source Code)
GPL-2.0C - Tiger VNC - High-performance, multi-platform VNC client and server. (Source Code)
GPL-2.0C++ - X2go - X2Go is an open source remote desktop software for Linux that uses the NoMachine/NX technology protocol. (Source Code)
GPL-2.0Perl
- Remmina - Feature-rich remote desktop application for linux and other unixes. (Source Code)
-
 @ c066aac5:6a41a034
2025-04-17 00:05:49
@ c066aac5:6a41a034
2025-04-17 00:05:49I am all about fleshing out a fantasy, even if the chances of it coming to reality are fairly slim. Dreams should be written down, meditated on, processed over long periods of time. I don't think of it as manifesting (nor do I condone manifestation); one could argue such practices are Biblical (Habakkuk 2:2).
So I'm going to write this out and make it plain, on the off chance that putting it out there brings somethings to fruition:
Jack Dorsey should take over Mozilla.
Either via an invitation from Mozilla, or via a hostile takeover. I don't really care how it happens, but I believe it should happen and I'll outline why.
The Fallen Hero

Mozilla has been having a bad time. I'm not sure that the organization has done much good since the unceremonious departure of Brenden Eich (there's Rust, but is that really a good thing?).
Firefox is losing its relevance. The FireFox Terms of Service update has sparked outrage, the removal of the promise to never sell your data was a Judas level of betrayal, FireFox currently (at the time this article was penned) makes up less than 3% of the total browser marketshare, their main source of income from Google is in jeopardy, most websites are only optimized for Chromium-based browsers, and the Gecko engine is not very secure.
Mozilla's best product is dying, and what is the organization doing about it? They're working on a plethora of issues their core user base does not care about. They've jumped on the AI hype train, they've bought an advertising company (which is very irrelevant to their user base, especially considering uBlock Orgin exists), they're selling white labeled VPNs (Mullvad), they're selling data removal services (which is powered by a former data broker), they're pushing shopping products, they're forcing features on their users which were never asked for (POCKET!!), it seems that Mozilla is completely out of touch with the people they claim to serve. They've abandoned their first love.
Thunderbird is showing some promise with the recent announcement of Thundermail, but that project will sadly suffer from guilt by association.
We have to remember though: Mozilla used to mean something in the FOSS/Open Source world.

They were the shining city on the hill of the internet. They rose up from the ashes of Netscape. FireFox kicked Internet Explorer's butt; it was a punk rock movement. Thunderbird is still an amazing email client. Rust (despite the arguing programmers) is a significant innovation in the programming language space.
I'm not rooting for the downfall of Mozilla. Sure, in a way I'd be happy about it: I'd like to see poor leadership get what it deserves, but I fear Mozilla as a symbol of FOSS/OS would send a sad signal across the ecosystem. I'm a capitalist at heart so I don't favor bailouts (nor am I calling for one); I truly believe this organization could be turned around with the right leadership. Maybe it could be as simple as going back to their original model of serving the deep pockets of the corporate world with open source tech rather than going for the wallets of the consumer.
Every problem is a leadership problem. Fix the leadership, fix the problems.
The Last Great Open Source Hero?
Sadly FOSS figures tend to die of public crucifixion. As time goes on, we have less and less great figures to point to. Thankfully, Jack hasn't been canceled yet.
Jack Dorsey has a pretty good résumé in the open source world. He jumped right in with Bitcoin. He left BlueSky for NOSTR. He would've made Twitter a protocol if he didn't need to feed himself early in his career. He is currently financing several projects in the Bitcoin and NOSTR world, which is arguably the best open source technology in the world right now.
I do believe that people should stay in their lane of expertise, and maybe Jack should. However, my message to Jack would be that it would be a shame if his passion for open source remained solely in Bitcoin and NOSTR. If his leadership was injected into the Mozilla machine, it could be steered into a magical direction.
Imagine FireFox being the first browser with layer 2 wallet integration (stick it to Brave and their BAT crap [we still love you Brenden Eich flaws and all]). Imagine having a whole world of existing talented developers suddenly interested in contributing their talents to the NOSTR community. Imagine having a browser with an engine that can actually go toe-to-toe with Chromium. Imagine an organization that once again gives FOSS a good name rather than actively eroding public confidence in FOSS.
The True FOSS Heroes

Jack is probably not going to touch Mozilla with a 150 foot pole (or see this article). We all probably need to let the Mozilla dream die in front of us.
Things aren't always black and white. I don't think of Mozilla as an evil organization; just an organization subject to the flaws of fellow humans like you and me. Even the Eye of Sauron, Google, has been a huge blessing to the open source world (Go programming language, Android, all of their open source sponsorships, many more things I could mention).
The beautiful thing about FOSS/OS is that it is a movement of the people. Titans will rise up and fall, but you and I make up the backbone of FOSS. I've had nothing but good interactions with FOSS fanatics. NOSTR's own OceanSlim taught me about Ungoogled Chromium, the Go programming language, and NOSTR relays. When I wanted to get into Linux, I was able to plug in immediately with a group of Linux users here in Nashville. NOSTR devs for the most part are happy to answer my inquiries when I slide into their DMs. I've been in group chats with people openly discussing the best way to make a great lightning wallet.
There's a lot of connection in the Open Source world that I cherish; it's very different from the corporate world most of us are immersed in. The corporate world has gatekeepers; Open Source has collaborators. The corporate world operates in the shadows to maximize profits; Open Source steps into the light for everyone's benefit. The corporate world says you'll never have enough experience/qualifications; Open Source encourages and equips you.
My point is, don't worship any organization. Be thankful for the people around you, try out FOSS programs whenever you can, and have fun with it.
All that said, I wouldn't mind if Jack took over Mozilla. Or if one of his friends took a position (ODELL?). Heck, throw Snowden in while we're at it.
Footnote: "Open Source" and "FOSS/Free and Open Source Software" are used interchangably in this article. Mistakes were made I'm sure, but I hope I got the point across.
-
 @ 6d5c826a:4b27b659
2025-05-23 21:48:56
@ 6d5c826a:4b27b659
2025-05-23 21:48:56- ActiveMQ - Java message broker. (Source Code)
Apache-2.0Java - BeanstalkD - A simple, fast work queue. (Source Code)
MITC - Gearman - Fast multi-language queuing/job processing platform. (Source Code)
BSD-3-ClauseC++ - NSQ - A realtime distributed messaging platform. (Source Code)
MPL-2.0Go - ZeroMQ - Lightweight queuing system. (Source Code)
GPL-3.0C++
- ActiveMQ - Java message broker. (Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:48:36
@ 6d5c826a:4b27b659
2025-05-23 21:48:36- aptly - Swiss army knife for Debian repository management. (Source Code)
MITGo - fpm - Versatile multi format package creator. (Source Code)
MITRuby - omnibus-ruby - Easily create full-stack installers for your project across a variety of platforms.
Apache-2.0Ruby - tito - Builds RPMs for git-based projects.
GPL-2.0Python
- aptly - Swiss army knife for Debian repository management. (Source Code)
-
 @ 1bc70a01:24f6a411
2025-04-16 13:53:00
@ 1bc70a01:24f6a411
2025-04-16 13:53:00I've been meaning to dogfood my own vibe project for a while so this feels like a good opportunity to use Untype to publish this update and reflect on my vibe coding journey.
New Untype Update
As I write this, I found it a bit annoying dealing with one of the latest features, so I'll need to make some changes right after I'm done. Nonetheless, here are some exciting developments in the Untype article composer:
-
Added inline AI helper! Now you can highlight text and perform all sorts of things like fix grammar, re-write in different styles, and all sorts of other things. This is a bit annoying at the moment because it takes over the other editing functions and I need to fix the UX.
-
Added pushing articles to DMs! This option, when enabled, will send the article to all the subscribers via a NIP-44 DM. (No client has implemented the subscription method yet so technically it won’t work, until one does. I may add this to nrss.app) Also, I have not tested this so it could be broken… will test eventually!
- Added word counts
- Added ability to export as markdown, export as PDF, print.
The biggest flaw I have already discovered is how "I" implemented the highlight functionality. Right now when you highlight some text it automatically pops up the AI helper menu and this makes for an annoying time trying to make any changes to text. I wanted to change this to show a floating clickable icon instead, but for some reason the bot is having a difficult time updating the code to this desired UX.
Speaking of difficult times, it's probably a good idea to reflect a bit upon my vibe coding journey.
Vibe Coding Nostr Projects
First, I think it's important to add some context around my recent batch of nostr vibe projects. I am working on them mostly at night and occasionally on weekends in between park runs with kids, grocery shopping and just bumming around the house. People who see buggy code or less than desired UX should understand that I am not spending days coding this stuff. Some apps are literally as simple as typing one prompt!
That said, its pretty clear by now that one prompt cannot produce a highly polished product. This is why I decided to limit my number of project to a handful that I really wish existed, and slowly update them over time - fixing bugs, adding new features in hopes of making them the best tools - not only on nostr but the internet in general. As you can imagine this is not a small task, especially for sporadic vibe coding.
Fighting the bot
One of my biggest challenges so far besides having very limited time is getting the bot to do what I want it to do. I guess if you've done any vibe coding at all you're probably familiar with what I'm trying to say. You prompt one thing and get a hallucinated response, or worse, a complete mess out the other end that undoes most of the progress you've made. Once the initial thing is created, which barely took any time, now you're faced with making it work a certain way. This is where the challenges arise.
Here's a brief list of issues I've faced when vibe-coding with various tools:
1. Runaway expenses - tools like Cline tend to do a better job directly in VSCode, but they can also add up dramatically. Before leaning into v0 (which is where I do most of my vibe coding now), I would often melt through $10 credit purchases faster than I could get a decent feature out. It was not uncommon for me to spend $20-30 on a weekend just trying to debug a handful of issues. Naturally, I did not wish to pay these fees so I searched for alternatives.
2. File duplication - occasionally, seemingly out of nowhere, the bot will duplicate files by creating an entire new copy and attached "-fixed" to the file name. Clearly, I'm not asking for duplicate files, I just want it to fix the existing file, but it does happen and it's super annoying. Then you are left telling it which version to keep and which one to delete, and sometimes you have to be very precise or it'll delete the wrong thing and you have to roll back to a previous working version.
3. Code duplication - similar to file duplication, occasionally the bot will duplicate code and do things in the most unintuitive way imaginable. This often results in loops and crashes that can take many refreshes just to revert back to a working state, and many more prompts to avoid the duplication entirely - something a seasoned dev never has to deal with (or so I imagine).
4. Misinterpreting your request - occasionally the bot will do something you didn't ask for because it took your request quite literally. This tends to happen when I give it very specific prompts that are targeted at fixing one very specific thing. I've noticed the bots tend to do better with vague asks - hence a pretty good result on the initial prompt.
5. Doing things inefficiently, without considering smarter approaches - this one is the most painful of vibe coding issues. As a person who may not be familiar with some of the smarter ways of handling development, you rely on the bot to do the right thing. But, when the bot does something horribly inefficiently and you are non-the-wiser, it can be tough to diagnose the issue. I often fight myself asking the bot "is this really the best way to handle things? Can't we ... / shouldn't we .../ isn't this supposed to..." etc. I guess one of the nice side effects of this annoyance is being able to prompt better. I learn that I should ask the bot to reflect on its own code more often and seek ways to do things more simply.
A combination of the above, or total chaos - this is a category where all hell breaks loose and you're trying to put out one fire after another. Fix one bug, only to see 10 more pop up. Fix those, to see 10 more and so on. I guess this may sound like typical development, but the bot amplifies issues by acting totally irrationally. This is typically when I will revert to a previous save point and just undo everything, often losing a lot of progress.
Lessons Learned
If I had to give my earlier self some tips on how to be a smarter vibe coder, here's how I'd summarize them:
-
Fork often - in v0 I now fork for any new major feature I'd like to add (such as the AI assistant).
-
Use targeting tools - in v0 you can select elements and describe how you wish to edit them.
-
Refactor often - keeping the code more manageable speeds up the process. Since the bot will go through the entire file, even if it only makes one small change, it's best to keep the files small and refactoring achieves that.
I guess the biggest lesson someone might point out is just to stop vibe coding. It may be easier to learn proper development and do things right. For me it has been a spare time hobby (one that I will admit is taking more of my extra time than I'd like). I don't really have the time to learn proper development. I feel like I've learned a lot just bossing the bot around and have learned a bunch of things in the process. That's not to say that I never will, but for the moment being my heart is still mostly in design. I haven't shared much of anything I have designed recently - mostly so I can remain speaking more freely without it rubbing off on my work.
I'll go ahead and try to publish this to see if it actually works 😂. Here goes nothing... (oh, I guess I could use the latest feature to export as markdown so I don't lose any progress! Yay!
-
-
 @ 6e0ea5d6:0327f353
2025-04-14 15:11:17
@ 6e0ea5d6:0327f353
2025-04-14 15:11:17Ascolta.
We live in times where the average man is measured by the speeches he gives — not by the commitments he keeps. People talk about dreams, goals, promises… but what truly remains is what’s honored in the silence of small gestures, in actions that don’t seek applause, in attitudes unseen — yet speak volumes.
Punctuality, for example. Showing up on time isn’t about the clock. It’s about respect. Respect for another’s time, yes — but more importantly, respect for one’s own word. A man who is late without reason is already running late in his values. And the one who excuses his own lateness with sweet justifications slowly gets used to mediocrity.
Keeping your word is more than fulfilling promises. It is sealing, with the mouth, what the body must later uphold. Every time a man commits to something, he creates a moral debt with his own dignity. And to break that commitment is to declare bankruptcy — not in the eyes of others, but in front of himself.
And debts? Even the small ones — or especially the small ones — are precise thermometers of character. A forgotten sum, an unpaid favor, a commitment left behind… all of these reveal the structure of the inner building that man resides in. He who neglects the small is merely rehearsing for his future collapse.
Life, contrary to what the reckless say, is not built on grand deeds. It is built with small bricks, laid with almost obsessive precision. The truly great man is the one who respects the details — recognizing in them a code of conduct.
In Sicily, especially in the streets of Palermo, I learned early on that there is more nobility in paying a five-euro debt on time than in flaunting riches gained without word, without honor, without dignity.
As they say in Palermo: L’uomo si conosce dalle piccole cose.
So, amico mio, Don’t talk to me about greatness if you can’t show up on time. Don’t talk to me about respect if your word is fickle. And above all, don’t talk to me about honor if you still owe what you once promised — no matter how small.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 6d5c826a:4b27b659
2025-05-23 21:48:21
@ 6d5c826a:4b27b659
2025-05-23 21:48:21- CapRover - Build your own PaaS in a few minutes. (Demo, Source Code)
Apache-2.0Docker/Nodejs - Coolify - An open-source & self-hostable Heroku / Netlify alternative (and even more). (Source Code)
Apache-2.0Docker - Dokku - An open-source PaaS (alternative to Heroku). (Source Code)
MITDocker/Shell/Go/deb - fx - A tool to help you do Function as a Service with painless on your own servers.
MITGo - Kubero - A self-hosted Heroku PaaS alternative for Kubernetes that implements GitOps. (Demo, Source Code)
GPL-3.0K8S/Nodejs/Go - LocalStack - LocalStack is a fully functional local AWS cloud stack. This includes Lambda for serverless computation. (Source Code)
Apache-2.0Python/Docker/K8S - Nhost - Firebase Alternative with GraphQL. Get a database and backend configured and ready in minutes. (Source Code)
MITDocker/Nodejs/Go - OpenFaaS - Serverless Functions Made Simple for Docker & Kubernetes. (Source Code)
MITGo - Tau - Easily build Cloud Computing Platforms with features like Serverless WebAssembly Functions, Frontend Hosting, CI/CD, Object Storage, K/V Database, and Pub-Sub Messaging. (Source Code)
BSD-3-ClauseGo/Rust/Docker - Trusted-CGI - Lightweight self-hosted lambda/applications/cgi/serverless-functions platform.
MITGo/deb/Docker
- CapRover - Build your own PaaS in a few minutes. (Demo, Source Code)
-
 @ 6d5c826a:4b27b659
2025-05-23 21:48:04
@ 6d5c826a:4b27b659
2025-05-23 21:48:04- GNS3 - Graphical network simulator that provides a variety of virtual appliances. (Source Code)
GPL-3.0Python - OpenWISP - Open Source Network Management System for OpenWRT based routers and access points. (Demo, Source Code)
GPL-3.0Python - Oxidized - Network device configuration backup tool.
Apache-2.0Ruby - phpIPAM - Open source IP address management with PowerDNS integration. (Source Code)
GPL-3.0PHP - RANCID - Monitor network devices configuration and maintain history of changes. (Source Code)
BSD-3-ClausePerl/Shell - rConfig - Network device configuration management tool. (Source Code)
GPL-3.0PHP
- GNS3 - Graphical network simulator that provides a variety of virtual appliances. (Source Code)
-
 @ c066aac5:6a41a034
2025-04-13 23:09:14
@ c066aac5:6a41a034
2025-04-13 23:09:14“If a man is considered guilty For what goes on in his mind Then give me the electric chair For all my future crimes”-Electric Chair by Prince
The very last paragraph of Touré’s 2013 biography of Prince I Would Die 4 U: Why Prince Became an Icon made a very bold claim about the lewd nature of Prince’s music:
“Imagine America as one house on a suburban lane… Prince knocked on America’s door through his music. He came to the door holding a guitar and an umbrella while concealing a Bible. He flirted his way inside the door and told us he had a dirty mind and was controversial, and then he sat down in the living room on the good couch. And, when America’s guard was down, because we thought we were having a conversation about sex, Prince eased out his Bible and said, let me also tell you about my Lord and savior, Jesus Christ.”
Wow. Talk about a Sixth Sense level plot twist! I will say if you’re well versed in Prince’s catalog (I listened to every Prince album released [except for The Black Album because Jack Dorsey is holding it hostage on Tidal] last year) it won’t be as shocking as a surprise as it would be to the unversed listener, but surprising nonetheless considering the content of the man’s lyrics (and life).
Regardless of whether or not Prince achieved this goal of bringing people to Christ via a vehicle of sexy shock value, he was a person of impact. The book by Touré I mentioned earlier is a great picture of the life he lived, and I’m sure there are many others that people can recommend in the comments. He touched many lives and I believe his music will still be listened to for many years to come.
Prince’s method of evangelism may have been unconventional (to say the least), but I still think there is something to be learned from his efforts.
Obviously, worshiping sex or encouraging lust isn’t great. Prince’s view of sex was broken; they didn’t line up with Biblically ordered sex (see his songs Sister, Darling Nikki, Sexy M.F., and many many more). His inability to sustain healthy relationships or make meaningful lasting connections with those around him are a testament to that.
Despite his flaws, his art captured an entire generation - and continues to capture the attention of people seeking true art. His authenticity, raw emotion, and intentionality made for true connection between his music and his listeners. He resonated with people’s souls, and still does today. Perhaps Touré was wrong and Prince didn’t mean to evangelize through his music, but don’t all people stand testament to the powerful work of God?
We are all broken people. Our job is to the use the tools and resources set before us to spread the Gospel. “…we have this treasure in clay jars, so that it may be made clear that this extraordinary power belongs to God and does not come from us.” -2 Corinthians 4:7
The Western Church should consider using the seemingly profane, off limits, unconventional, or even just plain weird in an effort to continue to spread the gospel. On a high level, that’s our good-christian dinner table no-gos: Sex, Money, and Politics. I believe that the Church’s abdication of such conversations is the reason why those are areas of failure for the Church at large. We shouldn’t sin or condone/promote sin. Instead, I’m proposing that like how Prince used sex in his music to get people to learn about Jesus, Christian Bitcoiners should use money (Bitcoin) to do good works and lead people to Jesus in the process. We may just make the world a better place along the way.
“If you're sick of cryin' and tired of tears Then close your eyes and open your ears Listen to the music, listen to the song Listen to your heart, is that so wrong? Stop lookin' in the mirror, there's nothin' to fear Your salvation is near 1,000 light years away from here”-1,000 Light Years From Here by Prince
It doesn’t take a lot of mental effort to see how Christian’s could leverage Bitcoin’s magic for kingdom work. Look Alex Gladstein’s writings. Look at the work that Gridless is doing in Africa. Look at Roya Mahboob’s impact in Afghanistan. Look at the impact of Bitcoin Beach in El Salvador.
Now imagine what the Church (and by the Church, I mean you and I the Christian Bitcoiners) could do with Bitcoin:
A Christian Bitcoiner could help the woman with an abusive husband escape a bad situation with finances intact by teaching her how to use Bitcoin and keep self-custody wallet. An orange-pilled youth group leader could teach the inner city kid in a bad household how to set up a wallet and stack sats without the permission of the dead beat parents or conventional employment. The church bake sale could make things easy via accepting lightning payments, bringing in outsiders for sweet treats and teaching them about how to be a Bitcoin merchant. A church could send funds to a missionary across the world in a christian adverse country instantly without having to involve a single bank, and that missionary would have those funds same-day ready for deployment.
“Everybody's looking for the ladder Everybody wants salvation of the soul The steps you take are no easy road But the reward is great For those who want to go”-The Ladder by Prince
In my own attempts to teach people about the virtues of Bitcoin, I find it usually clicks for people in one of two different ways for the most part:
The first way it clicks is when they can receive and send a lightning payment. The instant funds make a light bulb go off.
The second way is when I show them the humanitarian impact that Bitcoin has had and is counting to have. The use of Bitcoin internationally as a means of humanitarian aid/sovereignty for the less fortunate should shut down any questions like “But what about (insert crapcoin)?” in an instant.
Much like how people get Bitcoin once they see it in action, I believe people will get Jesus when they see Jesus’ Church in action. One of the best ways today the Church can display that action may be through Bitcoin.
Sex was Prince’s trojan horse for something much deeper that he wanted to convey to people. Bitcoin can be the trojan horse for the Church. The Church could gain attention for what they’re doing with Bitcoin similar to the attention that the Human Rights Foundation gets. One might ask why use a trojan horse? I think that Bitcoin adoption itself has been a bit of a trojan horse movement. Your local politicians didn’t bat an eye when they heard about a peer-to-peer e-cash system, but they were all over it when it was presented as a digital gold. Michael Saylor has garnered a lot of hate from the Bitcoin true-believers for presenting Bitcoin as a digital gold as opposed to a currency, but I believe he knows what he’s doing and he’s presenting in this manner on purpose. He might not get gratitude for it from the community, but I believe he’s willing to be the bad guy in order to further the mission (see Christopher Nolan’s The Dark Night [which is arguably a Jesus story]).
Christian Bitcoiner, I challenge you to channel your enthusiasm to do good in your neighborhood. Let the world see your actions and gain a curiosity for what you’re doing. The Bitcoin conversation will make many people think that you’re crazy, that you’re an idiot when it comes to investing, that you’re selling a scam. Much like how people wrote off Prince for being a vulgar musician. Much like how people write off Michael Saylor for misunderstanding Bitcoin. Much like how people wrote off (and continue to write off) Jesus for being a false prophet or the leader of a rebellion.
But there will be someone who sees the work that you do with Bitcoin. The work that the Church will do with Bitcoin. Even if just one soul is saved with Bitcoin, that’s worth the effort.
“Black day, stormy night No love, no hope in sight Don't cry, He is coming Don't die without knowing the cross” -The Cross by Prince
This article was written with help from my wife Elaina freedom@happytavern.co
Feel free to drop your favorite book about Prince, favorite Prince song, or favorite Prince album in the comments
Or, you can drop your favorite Bitcoin as a trojan horse story in the comments
