-
 @ b0a838f2:34ed3f19
2025-05-23 17:51:36
@ b0a838f2:34ed3f19
2025-05-23 17:51:36- ejabberd - XMPP instant messaging server. (Source Code)
GPL-2.0Erlang/Docker - MongooseIM - Mobile messaging platform with a focus on performance and scalability. (Source Code)
GPL-2.0Erlang/Docker/K8S - Openfire - Real time collaboration (RTC) server. (Source Code)
Apache-2.0Java - Prosody IM - Feature-rich and easy to configure XMPP server. (Source Code)
MITLua - Snikket - All-in-one Dockerized easy XMPP solution, including web admin and clients. (Source Code, Clients)
Apache-2.0Docker - Tigase - XMPP server implementation in Java. (Source Code)
GPL-3.0Java
- ejabberd - XMPP instant messaging server. (Source Code)
-
 @ b0a838f2:34ed3f19
2025-05-23 17:51:16
@ b0a838f2:34ed3f19
2025-05-23 17:51:16- BigBlueButton - Supports real-time sharing of audio, video, slides (with whiteboard controls), chat, and the screen. Instructors can engage remote students with polling, emojis, and breakout rooms. (Source Code)
LGPL-3.0Java - Galene - Video conferencing server that is easy to deploy and that requires moderate server resources. (Source Code)
MITGo - Janus - General-purpose, lightweight, minimalist WebRTC Server. (Demo, Source Code)
GPL-3.0C - Jitsi Meet - WebRTC application that uses Jitsi Videobridge to provide high quality, scalable video conferences. (Demo, Source Code)
Apache-2.0Nodejs/Docker/deb - Jitsi Video Bridge - WebRTC compatible Selective Forwarding Unit (SFU) that allows for multiuser video communication. (Source Code)
Apache-2.0Java/deb - MiroTalk C2C - Real-time cam-2-cam video calls & screen sharing, end-to-end encrypted, to embed in any website with a simple iframe. (Source Code)
AGPL-3.0Nodejs/Docker - MiroTalk P2P - Simple, secure, fast real-time video conferences up to 4k and 60fps, compatible with all browsers and platforms. (Demo, Source Code)
AGPL-3.0Nodejs/Docker - MiroTalk SFU - Simple, secure, scalable real-time video conferences up to 4k, compatible with all browsers and platforms. (Demo, Source Code)
AGPL-3.0Nodejs/Docker - plugNmeet - Scalable and high performance web conferencing system. (Demo, Source Code)
MITDocker/Go
- BigBlueButton - Supports real-time sharing of audio, video, slides (with whiteboard controls), chat, and the screen. Instructors can engage remote students with polling, emojis, and breakout rooms. (Source Code)
-
 @ b0a838f2:34ed3f19
2025-05-23 17:50:59
@ b0a838f2:34ed3f19
2025-05-23 17:50:59- Akkoma - Federated microblogging server with Mastodon, GNU social, and ActivityPub compatibility. (Source Code)
AGPL-3.0Elixir/Docker - Answer - Knowledge-based community software. You can use it to quickly build your Q&A community for product technical support, customer support, user communication, and more. (Source Code)
Apache-2.0Docker/Go - Artalk - Comment system built in Golang, providing a lightweight and highly customizable solution for adding comments to your website. (Source Code)
MITGo/Docker - AsmBB - Fast, SQLite-powered forum engine written in ASM. (Source Code)
EUPL-1.2Assembly - BuddyPress - Powerful plugin that takes your WordPress.org powered site beyond the blog with social-network features like user profiles, activity streams, user groups, and more. (Source Code)
GPL-2.0PHP - Chirpy - Privacy-friendly and customizable Disqus (comment system) alternate. (Demo, Source Code)
AGPL-3.0Docker/Nodejs - Coral - A better commenting experience from Vox Media. (Source Code)
Apache-2.0Docker/Nodejs - diaspora* - Distributed social networking server. (Source Code)
AGPL-3.0Ruby - Discourse - Advanced forum / community solution based on Ruby and JS. (Demo, Source Code)
GPL-2.0Docker - Elgg - Powerful open source social networking engine. (Source Code)
GPL-2.0PHP - Enigma 1/2 BBS - Enigma 1/2 is a modern, multi-platform BBS engine with unlimited "callers" and legacy DOS door game support. (Source Code)
BSD-2-ClauseShell/Docker/Nodejs - Flarum - Delightfully simple forums. Flarum is the next-generation forum software that makes online discussion fun again. (Source Code)
MITPHP - Friendica - Social Communication Server. (Source Code)
AGPL-3.0PHP - GoToSocial - ActivityPub federated social network server implementing the Mastodon client API. (Source Code)
AGPL-3.0Docker/Go - Hatsu - Bridge that interacts with Fediverse on behalf of your static site. (Source Code)
AGPL-3.0Docker/Rust - Hubzilla - Decentralized identity, privacy, publishing, sharing, cloud storage, and communications/social platform. (Source Code)
MITPHP - HumHub - Flexible kit for private social networks. (Source Code)
AGPL-3.0PHP - Isso - Lightweight commenting server written in Python and Javascript. It aims to be a drop-in replacement for Disqus. (Source Code)
MITPython/Docker - Lemmy - Link aggregator for the fediverse (alternative to Reddit). (Source Code)
AGPL-3.0Docker/Rust - Loomio - Collaborative decision-making tool that makes it easy for anyone to participate in decisions which affect them. (Source Code)
AGPL-3.0Docker - Mastodon - Federated microblogging server. (Source Code, Clients)
AGPL-3.0Ruby - Misago - Fully featured modern forum application that is fast, scalable and responsive. (Source Code)
GPL-2.0Docker - Misskey - Decentralized app-like microblogging server/SNS for the Fediverse, using the ActivityPub protocol like GNU social and Mastodon. (Source Code)
AGPL-3.0Nodejs/Docker - Movim - Modern, federated social network based on XMPP, with a fully featured group-chat, subscriptions and microblogging. (Source Code)
AGPL-3.0PHP/Docker - MyBB - Free, extensible forum software package. (Source Code)
LGPL-3.0PHP - NodeBB - Forum software built for the modern web. (Demo, Source Code)
GPL-3.0Nodejs/Docker - OSSN - Social networking software that allows you to make a social networking website and helps your members build social relationships, with people who share similar professional or personal interests. (Source Code)
CAL-1.0PHP - phpBB - Flat-forum bulletin board software solution that can be used to stay in touch with a group of people or can power your entire website. (Source Code)
GPL-2.0PHP - PixelFed - Ethical photo sharing platform, powered by ActivityPub federation (alternative to Instagram). (Source Code)
AGPL-3.0PHP - Pleroma - Federated microblogging server, Mastodon, GNU social, & ActivityPub compatible. (Source Code)
AGPL-3.0Elixir - qpixel - Q&A-based community knowledge-sharing software. (Source Code)
AGPL-3.0Ruby - Redlib
⚠- An alternative private front-end to Reddit, with its origins in Libreddit.AGPL-3.0Rust - remark42 - A lightweight and simple comment engine, which doesn't spy on users. It can be embedded into blogs, articles or any other place where readers add comments. (Demo, Source Code)
MITDocker/Go - Retrospring - A free, open-source social network following the Q/A (question and answer) principle of sites like Formspring, ask.fm or CuriousCat. (Demo)
AGPL-3.0Ruby/Nodejs - Scoold - Stack Overflow in a JAR. An enterprise-ready Q&A platform with full-text search, SAML, LDAP integration and social login support. (Demo, Source Code)
Apache-2.0Java/Docker/K8S - Simple Machines Forum - Free, professional grade software package that allows you to set up your own online community within minutes. (Source Code)
BSD-3-ClausePHP - Socialhome - Federated and decentralized profile builder and social network engine. (Demo, Source Code)
AGPL-3.0Docker/Python - Takahē - Federated microblogging server. Mastodon, & ActivityPub compatible. (Source Code)
BSD-3-ClauseDocker - Talkyard - Create a community, where your users can suggest ideas and get questions answered. And have friendly open-ended discussions and chat (Slack/StackOverflow/Discourse/Reddit/Disqus hybrid). (Demo, Source Code)
AGPL-3.0Docker/Scala - yarn.social - Self-Hosted, Twitter™-like Decentralised micro-logging platform. No ads, no tracking, your content, your data. (Source Code)
MITGo - Zusam - Free and open-source way to self-host private forums for groups of friends or family. (Demo)
AGPL-3.0PHP
- Akkoma - Federated microblogging server with Mastodon, GNU social, and ActivityPub compatibility. (Source Code)
-
 @ b0a838f2:34ed3f19
2025-05-23 17:50:31
@ b0a838f2:34ed3f19
2025-05-23 17:50:31- Asterisk - Easy to use but advanced IP PBX system, VoIP gateway and conference server. (Source Code)
GPL-2.0C/deb - Eqivo - Eqivo implements an API layer on top of FreeSWITCH facilitating integration between web applications and voice/video-enabled endpoints such as traditional phone lines (PSTN), VoIP phones, webRTC clients etc. (Source Code)
MITDocker/PHP - Flexisip - Complete, modular and scalable SIP server, includes a push gateway, to deliver SIP incoming calls or text messages on mobile device platforms where push notifications are required to receive information when the app is not active in the foreground. (Source Code)
AGPL-3.0C/Docker - Freepbx - Web-based open source GUI that controls and manages Asterisk. (Source Code)
GPL-2.0PHP - FreeSWITCH - Scalable open source cross-platform telephony platform. (Source Code)
MPL-2.0C - FusionPBX - Web interface for multi-platform voice switch called FreeSWITCH. (Source Code)
MPL-1.1PHP - Kamailio - Modular SIP server (registrar/proxy/router/etc). (Source Code)
GPL-2.0C/deb - openSIPS - SIP proxy/server for voice, video, IM, presence and any other SIP extensions. (Source Code)
GPL-2.0C - Routr - A lightweight sip proxy, location server, and registrar for a reliable and scalable SIP infrastructure. (Source Code)
MITDocker/K8S - SIP3 - VoIP troubleshooting and monitoring platform. (Demo, Source Code)
Apache-2.0Java - SIPCAPTURE Homer - Troubleshooting and monitoring VoIP calls. (Source Code)
AGPL-3.0Nodejs/Go/Docker - Wazo - Full-featured IPBX solution built atop Asterisk with integrated Web administration interface and REST-ful API. (Source Code)
GPL-3.0Python - Yeti-Switch - Transit class4 softswitch(SBC) with integrated billing and routing engine and REST API. (Demo, Source Code)
GPL-2.0C++/Ruby
- Asterisk - Easy to use but advanced IP PBX system, VoIP gateway and conference server. (Source Code)
-
 @ b0a838f2:34ed3f19
2025-05-23 17:50:11
@ b0a838f2:34ed3f19
2025-05-23 17:50:11- Convos - Always online web IRC client. (Demo, Source Code)
Artistic-2.0Perl/Docker - Ergo - Modern IRCv3 server written in Go, combining the features of an ircd, a services framework, and a bouncer. (Source Code)
MITGo/Docker - Glowing Bear - A web frontend for WeeChat. (Demo)
GPL-3.0Nodejs - InspIRCd - Modular IRC server written in C++ for Linux, BSD, Windows, and macOS. (Source Code)
GPL-2.0C++/Docker - Kiwi IRC - Responsive web IRC client with theming support. (Demo, Source Code)
Apache-2.0Nodejs - ngircd - Portable and lightweight Internet Relay Chat server for small or private networks. (Source Code)
GPL-2.0C/deb - Quassel IRC - Distributed IRC client, meaning that one (or multiple) client(s) can attach to and detach from a central core. (Source Code)
GPL-2.0C++ - Robust IRC - RobustIRC is IRC without netsplits. Distributed IRC server, based on RobustSession protocol. (Source Code)
BSD-3-ClauseGo - The Lounge - Self-hosted web IRC client. (Demo, Source Code)
MITNodejs/Docker - UnrealIRCd - Modular, advanced and highly configurable IRC server written in C for Linux, BSD, Windows, and macOS. (Source Code)
GPL-2.0C - Weechat - Fast, light and extensible chat client. (Source Code)
GPL-3.0C/Docker/deb - ZNC - Advanced IRC bouncer. (Source Code)
Apache-2.0C++/deb
- Convos - Always online web IRC client. (Demo, Source Code)
-
 @ b0a838f2:34ed3f19
2025-05-23 17:49:53
@ b0a838f2:34ed3f19
2025-05-23 17:49:53- Cypht - Feed reader for your email accounts. (Source Code)
LGPL-2.1PHP - Roundcube - Browser-based IMAP client with an application-like user interface. (Source Code)
GPL-3.0PHP/deb - SnappyMail - Simple, modern, lightweight & fast web-based email client (fork of RainLoop). (Demo, Source Code)
AGPL-3.0PHP - SquirrelMail - Another browser-based IMAP client. (Source Code)
GPL-2.0PHP
- Cypht - Feed reader for your email accounts. (Source Code)
-
 @ b0a838f2:34ed3f19
2025-05-23 17:49:32
@ b0a838f2:34ed3f19
2025-05-23 17:49:32- HyperKitty - Access GNU Mailman v3 archives. (Demo, Source Code)
GPL-3.0Python - Keila - Reliable and easy-to-use newsletter tool (alternative to Mailchimp or Sendinblue). (Demo, Source Code)
AGPL-3.0Docker - Listmonk - High performance, self-hosted newsletter and mailing list manager with a modern dashboard. (Source Code)
AGPL-3.0Go/Docker - Mailman - Manage electronic mail discussion and e-newsletter lists. (Source Code)
GPL-3.0Python - Mautic - Marketing automation software (email, social and more). (Source Code)
GPL-3.0PHP - phpList - Newsletter and email marketing with advanced management of subscribers, bounces, and plugins. (Source Code)
AGPL-3.0PHP - Postorius - Web user interface to access GNU Mailman. (Source Code)
GPL-3.0Python - Schleuder - GPG-enabled mailing list manager with resending-capabilities. (Source Code)
GPL-3.0Ruby - Sympa - Mailing list manager. (Source Code)
GPL-2.0Perl
- HyperKitty - Access GNU Mailman v3 archives. (Demo, Source Code)
-
 @ b0a838f2:34ed3f19
2025-05-23 17:49:07
@ b0a838f2:34ed3f19
2025-05-23 17:49:07- chasquid - SMTP (email) server with a focus on simplicity, security, and ease of operation. (Source Code)
Apache-2.0Go - Courier MTA - Fast, scalable, enterprise mail/groupware server providing ESMTP, IMAP, POP3, webmail, mailing list, basic web-based calendaring and scheduling services. (Source Code)
GPL-3.0C/deb - DragonFly - A small MTA for home and office use. Works on Linux and FreeBSD.
BSD-3-ClauseC - EmailRelay - A small and easy to configure SMTP and POP3 server for Windows and Linux. (Source Code)
GPL-3.0C++ - Exim - Message transfer agent (MTA) developed at the University of Cambridge. (Source Code)
GPL-3.0C/deb - Haraka - Fast, highly extensible, and event driven SMTP server. (Source Code)
MITNodejs - MailCatcher - Deploy a simply SMTP MTA gateway that accepts all mail and displays in web interface. Useful for debugging or development. (Source Code)
MITRuby - OpenSMTPD - Secure SMTP server implementation from the OpenBSD project. (Source Code)
ISCC/deb - OpenTrashmail - Complete trashmail solution that exposes an SMTP server and has a web interface to manage received emails. Works with multiple and wildcard domains and is fully file based (no database needed). Includes RSS feeds and JSON API.
Apache-2.0Python/PHP/Docker - Postfix - Fast, easy to administer, and secure Sendmail replacement.
IPL-1.0C/deb - Sendmail - Message transfer agent (MTA).
SendmailC/deb
- chasquid - SMTP (email) server with a focus on simplicity, security, and ease of operation. (Source Code)
-
 @ b0a838f2:34ed3f19
2025-05-23 17:48:32
@ b0a838f2:34ed3f19
2025-05-23 17:48:32- Cyrus IMAP - Email (IMAP/POP3), contacts and calendar server. (Source Code)
BSD-3-Clause-AttributionC - DavMail
⚠- POP/IMAP/SMTP/Caldav/Carddav/LDAP exchange gateway allowing users to use any mail/calendar client with an Exchange server, even from the internet or behind a firewall through Outlook Web Access. (Source Code)GPL-2.0Java - Dovecot - IMAP and POP3 server written primarily with security in mind. (Source Code)
MIT/LGPL-2.1C/deb - Piler - Feature-rich email archiving solution. (Source Code)
GPL-3.0C
- Cyrus IMAP - Email (IMAP/POP3), contacts and calendar server. (Source Code)
-
 @ b0a838f2:34ed3f19
2025-05-23 17:48:10
@ b0a838f2:34ed3f19
2025-05-23 17:48:10- AnonAddy - Email forwarding service for creating aliases. (Source Code)
MITPHP/Docker - DebOps - Your Debian-based data center in a box. A set of general-purpose Ansible roles that can be used to manage Debian or Ubuntu hosts. (Source Code)
GPL-3.0Ansible/Python - docker-mailserver - Production-ready fullstack but simple mail server (SMTP, IMAP, LDAP, Antispam, Antivirus, etc.) running inside a container. Only configuration files, no SQL database. (Source Code)
MITDocker - Dovel - SMTP server that sends and receives emails according to a simple configuration file, with an optional web interface that you can use to browse your emails. (Source Code)
LGPL-3.0Go - emailwiz - Luke Smith's bash script to completely automate the setup of a Postfix/Dovecot/SpamAssassin/OpenDKIM server on debian.
GPL-3.0Shell - homebox - Suite of Ansible scripts to deploy a fully functional mail server on Debian. Unobtrusive and automatic as much as possible, focusing on stability and security.
GPL-3.0Shell - Inboxen - Lets you have an infinite number of unique inboxes. (Source Code)
GPL-3.0Python - iRedMail - Full-featured mail server solution based on Postfix and Dovecot. (Source Code)
GPL-3.0Shell - Maddy Mail Server - All-in-one mail server that implements SMTP (both MTA and MX) and IMAP. Replaces Postfix, Dovecot, OpenDKIM, OpenSPF, OpenDMARC with single daemon. (Source Code)
GPL-3.0Go - Mail-in-a-Box - Turns any Ubuntu server into a fully functional mail server with one command. (Source Code)
CC0-1.0Shell - Mailcow - Mail server suite based on Dovecot, Postfix and other open source software, that provides a modern Web UI for administration. (Source Code)
GPL-3.0Docker/PHP - Mailu - Simple yet full-featured mail server as a set of Docker images. (Source Code)
MITDocker/Python - Modoboa - Mail hosting and management platform including a modern and simplified web user interface. (Source Code)
ISCPython - Mox - Complete e-mail solution with IMAP4, SMTP, SPF, DKIM, DMARC, MTA-STS, DANE and DNSSEC, reputation-based and content-based junk filtering, Internationalization (IDNA), automatic TLS with ACME and Let's Encrypt, account autoconfiguration, and webmail. (Source Code)
MITGo - Postal - Complete and fully featured mail server for use by websites & web servers. (Source Code)
MITDocker/Ruby - Simple NixOS Mailserver - Complete mailserver solution leveraging the Nix Ecosystem.
GPL-3.0Nix - SimpleLogin - Open source email alias solution to protect your email address. Comes with browser extensions and mobile apps. (Source Code)
MITDocker/Python - Stalwart Mail Server - All-in-one mail server with JMAP, IMAP4, and SMTP support and a wide range of modern features. (Source Code)
AGPL-3.0Rust/Docker - wildduck - Scalable no-SPOF IMAP/POP3 mail server. (Source Code)
EUPL-1.2Nodejs/Docker
- AnonAddy - Email forwarding service for creating aliases. (Source Code)
-
 @ b0a838f2:34ed3f19
2025-05-23 17:47:51
@ b0a838f2:34ed3f19
2025-05-23 17:47:51- AnyCable - Realtime server for reliable two-way communication over WebSockets, Server-sent events, etc. (Demo, Source Code)
MITGo/Docker - Apprise - Apprise allows you to send a notification to almost all of the most popular notification services available to us today such as: Telegram, Discord, Slack, Amazon SNS, Gotify, etc.
MITPython/Docker/deb - Centrifugo - Language-agnostic real-time messaging (Websocket or SockJS) server. (Demo, Source Code)
MITGo/Docker/K8S - Chitchatter - Peer-to-peer chat app that is serverless, decentralized, and ephemeral. (Source Code)
GPL-2.0Nodejs - Conduit - A simple, fast, and reliable chat server powered by Matrix. (Source Code)
Apache-2.0Rust - Databag - Federated, end-to-end encrypted messaging service for the web, iOS, and Android, supporting text, photos, video, and WebRTC video and audio calls. (Demo)
Apache-2.0Docker - Element - Fully-featured Matrix client for Web, iOS & Android. (Source Code)
Apache-2.0Nodejs - GlobaLeaks - Whistleblowing software enabling anyone to easily set up and maintain a secure reporting platform. (Demo, Source Code)
AGPL-3.0Python/deb/Docker - GNUnet - Software framework for decentralized, peer-to-peer networking. (Source Code)
GPL-3.0C - Gotify - Notification server with Android and CLI clients (alternative to PushBullet). (Source Code, Clients)
MITGo/Docker - Hyphanet - Anonymously share files, browse and publish freesites (web sites accessible only through Hyphanet) and chat on forums. (Source Code)
GPL-2.0Java - Jami - Universal communication platform which preserves the user's privacy and freedoms. (Source Code)
GPL-3.0C++ - Live Helper Chat - Live Support chat for your website. (Source Code)
Apache-2.0PHP - Mattermost - Platform for secure collaboration across the entire software development lifecycle, can be integrated with Gitlab (alternative to Slack). (Source Code)
AGPL-3.0/Apache-2.0Go/Docker/K8S - MiAOU - Multi-room persistent chat server. (Source Code)
MITNodejs - Mumble - Low-latency, high quality voice/text chat software. (Source Code, Clients)
BSD-3-ClauseC++/deb - Notifo - Multichannel notification server with support for Email, Mobile Push, Web Push, SMS, messaging and a javascript plugin.
MITC# - Novu - Notification infrastructure for developers. (Source Code)
MITDocker/Nodejs - ntfy - Push notifications to phone or desktop using HTTP PUT/POST, with Android app, CLI and web app, similar to Pushover and Gotify. (Demo, Source Code, Clients)
Apache-2.0/GPL-2.0Go/Docker/K8S - One Time Secret - Share sensitive information securely with self-destructing links that are only viewable once. (Demo, Source Code)
MITDocker/Ruby/Nodejs - OTS - One-Time-Secret sharing platform with a symmetric 256bit AES encryption in the browser. (Source Code)
Apache-2.0Go - PushBits - Notification server for relaying push notifications via Matrix, similar to PushBullet and Gotify.
ISCGo - RetroShare - Secured and decentralized communication system. Offers decentralized chat, forums, messaging, file transfer. (Source Code)
GPL-2.0C++ - Revolt - Revolt is a user-first chat platform built with modern web technologies. (Source Code)
AGPL-3.0Rust - Rocket.Chat - Teamchat solution similar to Gitter.im or Slack. (Source Code)
MITNodejs/Docker/K8S - SAMA - Next-Gen self-hosted chat server and clients. (Demo, Source Code, Clients)
GPL-3.0Nodejs/Docker - Screego - Screego is a simple tool to quickly share your screen to one or multiple people via web browser. (Demo, Source Code)
GPL-3.0Docker/Go - Shhh - Keep secrets out of emails or chat logs, share them using secure links with passphrase and expiration dates.
MITPython - SimpleX Chat - The most private and secure chat and applications platform - now with double ratchet E2E encryption.
AGPL-3.0Haskell - Spectrum 2 - Spectrum 2 is an open source instant messaging transport. It allows users to chat together even when they are using different IM networks. (Source Code)
GPL-3.0C++ - Synapse - Server for Matrix, an open standard for decentralized persistent communication. (Source Code)
Apache-2.0Python/deb - Syndie - Syndie is a libre system for operating distributed forums.
CC0-1.0Java - Tailchat - Next generation noIM application in your own workspace, not only another Slack/Discord/rocket.chat. (Demo, Source Code)
Apache-2.0Docker/K8S/Nodejs - Tiledesk - All-in-one customer engagement platform from lead-gen to post-sales, from WhatsApp to your website. With omni-channel live agents and AI-powered chatbots (alternative to Intercom, Zendesk, Tawk.to and Tidio). (Source Code)
MITDocker/K8S - Tinode - Instant messaging platform. Backend in Go. Clients: Swift iOS, Java Android, JS webapp, scriptable command line; chatbots. (Demo, Source Code, Clients)
GPL-3.0Go - Tox - Distributed, secure messenger with audio and video chat capabilities. (Source Code)
GPL-3.0C - Typebot - Conversational app builder (alternative to Typeform or Landbot). (Source Code)
AGPL-3.0Docker - WBO - Web Whiteboard to collaborate in real-time on schemas, drawings, and notes. (Demo)
AGPL-3.0Nodejs/Docker - Zulip - Zulip is a powerful, open source group chat application. (Source Code)
Apache-2.0Python
- AnyCable - Realtime server for reliable two-way communication over WebSockets, Server-sent events, etc. (Demo, Source Code)
-
 @ b0a838f2:34ed3f19
2025-05-23 17:47:26
@ b0a838f2:34ed3f19
2025-05-23 17:47:26- Baïkal - Lightweight CalDAV and CardDAV server based on sabre/dav. (Source Code)
GPL-3.0PHP - DAViCal - Server for calendar sharing (CalDAV) that uses a PostgreSQL database as a data store. (Source Code)
GPL-2.0PHP/deb - Davis - A simple, dockerizable and fully translatable admin interface for sabre/dav based on Symfony 5 and Bootstrap 4, largely inspired by Baïkal.
MITPHP - Etebase (EteSync) - End-to-end encrypted and journaled personal information server supporting calendar and contact data, offering its own clients. (Source Code)
AGPL-3.0Python/Django - Manage My Damn Life - Manage my Damn Life (MMDL) is a self-hosted front end for managing your CalDAV tasks and calendars. (Source Code)
GPL-3.0Nodejs/Docker - Radicale - Simple calendar and contact server with extremely low administrative overhead. (Source Code)
GPL-3.0Python/deb - SabreDAV - Open source CardDAV, CalDAV, and WebDAV framework and server. (Source Code)
MITPHP - Xandikos - Open source CardDAV and CalDAV server with minimal administrative overhead, backed by a Git repository.
GPL-3.0Python/deb
- Baïkal - Lightweight CalDAV and CardDAV server based on sabre/dav. (Source Code)
-
 @ b0a838f2:34ed3f19
2025-05-23 17:47:03
@ b0a838f2:34ed3f19
2025-05-23 17:47:03- Briefkasten - Modern app for saving and managing your own bookmarks. Includes a browser extension. (Demo)
MITNodejs/Docker - Buku - Powerful bookmark manager and a personal textual mini-web.
GPL-3.0Python/deb - Digibunch - Create bunches of links to share with your learners or colleagues. (Demo, Source Code)
AGPL-3.0Nodejs/PHP - Espial - An open-source, web-based bookmarking server.
AGPL-3.0Haskell - Firefox Account Server - Host your own Firefox accounts server. (Source Code)
MPL-2.0Nodejs/Java - Grimoire - Bookmark manager with a modern UI, automatic content & metadata extraction, categorization, filtering, and more. It has fully documented REST API, and Docker image for easy deployment. (Source Code)
MITNodejs/Docker - Karakeep - Bookmark-everything app with a touch of AI for the data hoarders out there. (Demo, Source Code)
AGPL-3.0Docker - LinkAce - Bookmark archive with automatic backups to the Internet Archive, link monitoring, and a full REST API. Installation is done via Docker, or as a simple PHP application. (Demo, Source Code)
GPL-3.0Docker/PHP - linkding - Minimal bookmark management with a fast and clean UI. Simple installation through Docker and can run on your Raspberry Pi. (Demo, Source Code)
MITDocker - LinkWarden - Bookmark and archive manager to store your useful links. (Source Code)
MITDocker/Nodejs - NeonLink - Bookmark service with unique design and simple installation with Docker.
MITDocker - Readeck - Readeck is a simple web application that lets you save the precious readable content of web pages you like and want to keep forever. See it as a bookmark manager and a read later tool. (Source Code, Clients)
AGPL-3.0Go/Docker - Servas - A self-hosted bookmark management tool. It allows organization with tags, groups, and a list specifically for later access. It supports multiple users with 2FA. Companion browser extensions are available for Firefox and Chrome. (Clients)
GPL-3.0Docker/Nodejs/PHP - Shaarli - Personal, minimalist, super-fast, no-database bookmarking and link sharing platform. (Demo)
ZlibPHP/deb - Shiori - Simple bookmark manager built with Go.
MITGo/Docker - Slash - An open source, self-hosted bookmarks and link sharing platform.
GPL-3.0Docker - SyncMarks - Sync and manage your browser bookmarks from Edge, Firefox and Chromium. (Clients)
AGPL-3.0PHP
- Briefkasten - Modern app for saving and managing your own bookmarks. Includes a browser extension. (Demo)
-
 @ b0a838f2:34ed3f19
2025-05-23 17:46:16
@ b0a838f2:34ed3f19
2025-05-23 17:46:16- Alf.io - Ticket reservation system. (Demo, Source Code)
GPL-3.0Java - Cal.com - Online appointment scheduling system. (Demo, Source Code)
AGPL-3.0Nodejs - Easy!Appointments - Allows your customers to book appointments with you via the web. (Demo, Source Code)
GPL-3.0PHP - Hi.Events - Event management and ticketing platform for conferences, concerts, and more. Offering customizable event pages and embeddable ticket widgets. (Demo, Source Code)
AGPL-3.0Docker - QloApps - Customizable and intuitive web-based hotel reservation system and a booking engine. (Demo, Source Code)
OSL-3.0PHP/Nodejs - Rallly - Create polls to vote on dates and times (alternative to Doodle). (Demo, Source Code)
AGPL-3.0Nodejs/Docker - Seatsurfing - Webbased app to book seats, desks and rooms for offices. (Source Code)
GPL-3.0Docker
- Alf.io - Ticket reservation system. (Demo, Source Code)
-
 @ b0a838f2:34ed3f19
2025-05-23 17:45:55
@ b0a838f2:34ed3f19
2025-05-23 17:45:55- Antville - Free, open source project aimed at the development of a high performance, feature rich weblog hosting software. (Source Code)
Apache-2.0Javascript - Castopod - Podcast management hosting platform that includes the latest podcast 2.0 standards, an automated Fediverse feed, analytics, an embeddable player, and more. (Source Code)
AGPL-3.0PHP/Docker - Chyrp Lite - Extra-awesome, extra-lightweight blog engine. (Source Code)
BSD-3-ClausePHP - Dotclear - Take control over your blog.
GPL-2.0PHP - FlatPress - A lightweight, easy-to-set-up flat-file blogging engine. (Source Code)
GPL-2.0PHP - Ghost - Just a blogging platform. (Source Code)
MITNodejs - Haven - Private blogging system with markdown editing and built in RSS reader. (Demo, Source Code)
MITRuby - HTMLy - Databaseless PHP blogging platform. A flat-file CMS that allows you to create a fast, secure, and powerful website or blog in seconds. (Demo, Source Code)
GPL-2.0PHP - Known - Collaborative social publishing platform. (Source Code)
Apache-2.0PHP - Mataroa - Naked blogging platform for minimalists. (Source Code)
MITPython - PluXml - XML-based blog/CMS platform. (Source Code)
GPL-3.0PHP - Serendipity - Serendipity (s9y) is a highly extensible and customizable PHP blog engine using Smarty templating. (Source Code)
BSD-3-ClausePHP - WriteFreely - Writing software for starting a minimalist, federated blog — or an entire community. (Source Code)
AGPL-3.0Go
- Antville - Free, open source project aimed at the development of a high performance, feature rich weblog hosting software. (Source Code)
-
 @ b0a838f2:34ed3f19
2025-05-23 17:45:36
@ b0a838f2:34ed3f19
2025-05-23 17:45:36- Activepieces - No-code business automation tool like Zapier or Tray. For example, you can send a Slack notification for each new Trello card. (Source Code)
MITDocker - Apache Airflow - Platform to programmatically author, schedule, and monitor workflows. (Source Code)
Apache-2.0Python/Docker - Automatisch - Business automation tool that lets you connect different services like Twitter, Slack, and more to automate your business processes (alternative to Zapier). (Source Code)
AGPL-3.0Docker - BookBounty
⚠- Retrieve missing Readarr books from Library Genesis.MPL-2.0Docker - changedetection.io - Stay up-to-date with web-site content changes. (Source Code)
Apache-2.0Python/Docker - ChiefOnboarding - Employee onboarding platform that allows you to provision user accounts and create sequences with todo items, resources, text/email/Slack messages, and more! Available as a web portal and Slack bot. (Source Code)
AGPL-3.0Docker - Discount Bandit
⚠- Track pricing, stock status of products across multiple stores such as Amazon, Ebay, Walmart, etc. (Source Code)GPL-3.0PHP/Docker - Dittofeed - Omni-channel customer engagement and messaging automation platform (alternative to Braze, Customer.io, Iterable). (Demo, Source Code)
MITDocker - feedmixer - Micro web service which takes a list of feed URLs and returns a new feed consisting of the most recent n entries from each given feed (returns Atom, RSS, or JSON). (Demo)
WTFPLPython - Github Ntfy
⚠- Push notifications to NTFY when a new release is available on Docker Hub or Github. (Clients)GPL-3.0Docker - HandBrake Web - Use one or more instances of HandBrake video transcoder on a headless device via a web interface.
AGPL-3.0Docker - Healthchecks - Listen for pings and sends alerts when pings are late. (Source Code)
BSD-3-ClausePython/Docker - HRConvert2 - Drag-and-drop file conversion server with session based authentication, automatic temporary file maintenance, and logging capability.
GPL-3.0PHP - Huginn - Build agents that monitor and act on your behalf.
MITRuby - Kestra - Event-driven, language-agnostic platform to create, schedule, and monitor workflows. In code. Coordinate data pipelines and tasks such as ETL and ELT. (Source Code)
Apache-2.0Docker - Kibitzr - Lightweight personal web assistant with powerful integrations. (Source Code)
MITPython - LazyLibrarian
⚠- Follow authors and grab metadata for all your digital reading needs. It uses a combination of Goodreads, Librarything and optionally GoogleBooks as sources for author info and book info.GPL-3.0Python - Leon - Personal assistant who can live on your server. (Source Code)
MITNodejs - Matchering - Automated music mastering (alternative to LANDR, eMastered, and MajorDecibel).
GPL-3.0Docker - Mylar3 - Automated Comic Book (cbr/cbz) downloader program for use with NZB and torrents. (Source Code)
GPL-3.0Python/Docker - OliveTin - Web interface for running Linux shell commands. (Source Code)
AGPL-3.0Go - pyLoad - Lightweight, customizable and remotely manageable downloader for 1-click-hosting sites like rapidshare.com or uploaded.to. (Source Code)
AGPL-3.0Python - StackStorm - StackStorm (aka IFTTT for Ops) is event-driven automation for auto-remediation, security responses, troubleshooting, deployments, and more. Includes rules engine, workflow, 160 integration packs with 6000+ actions and ChatOps. (Source Code)
Apache-2.0Python - µTask - Automation engine that models and executes business processes declared in yaml.
BSD-3-ClauseGo/Docker
- Activepieces - No-code business automation tool like Zapier or Tray. For example, you can send a Slack notification for each new Trello card. (Source Code)
-
 @ b0a838f2:34ed3f19
2025-05-23 17:45:10
@ b0a838f2:34ed3f19
2025-05-23 17:45:10- ArchiveBox - Create HTML & screenshot archives of sites from your bookmarks, browsing history, RSS feeds, or other sources (alternative to Wayback Machine). (Source Code)
MITPython/Docker - ArchivesSpace - Archives information management application for managing and providing Web access to archives, manuscripts and digital objects. (Demo, Source Code)
ECL-2.0Ruby - bitmagnet - BitTorrent indexer, DHT crawler, content classifier and torrent search engine with web UI, GraphQL API and Servarr stack integration. (Source Code)
MITGo/Docker - CKAN - Make open data websites. (Source Code)
AGPL-3.0Python - Collective Access - Providence - Highly configurable Web-based framework for management, description, and discovery of digital and physical collections supporting a variety of metadata standards, data types, and media formats. (Source Code)
GPL-3.0PHP - Ganymede
⚠- Twitch VOD and live stream archiving platform. Includes a rendered chat for each archive.GPL-3.0Docker - LiveStreamDVR
⚠- Automatic Twitch recorder capable of capturing live streams, chat messages and stream metadata.MITPython/Nodejs/Docker - Omeka S - next-generation web publishing platform for institutions interested in connecting digital cultural heritage collections with other resources online. (Source Code)
GPL-3.0Nodejs - Wallabag - Wallabag, formerly Poche, is a web application allowing you to save articles to read them later with improved readability. (Source Code)
MITPHP - Wayback - A self-hosted toolkit for archiving webpages to the Internet Archive, archive.today, IPFS, and local file systems.
GPL-3.0Go - Webarchive - Lightweight self-hosted wayback machine that creates HTML and PDF files from your bookmarks.
BSD-3-ClauseGo
- ArchiveBox - Create HTML & screenshot archives of sites from your bookmarks, browsing history, RSS feeds, or other sources (alternative to Wayback Machine). (Source Code)
-
 @ b0a838f2:34ed3f19
2025-05-23 17:44:31
@ b0a838f2:34ed3f19
2025-05-23 17:44:31- Aptabase - Privacy first and simple analytics for mobile and desktop apps. (Source Code)
AGPL-3.0Docker - AWStats - Generate statistics from web, streaming, ftp or mail server logfiles. (Demo, Source Code)
GPL-3.0Perl - Countly Community Edition - Real time mobile and web analytics, crash reporting and push notifications platform. (Source Code)
AGPL-3.0Nodejs/Docker - Daily Stars Explorer
⚠- Track GitHub repo trends with daily star insights to see growth and community interest over time. (Demo, Source Code)MITGo/Nodejs/Docker - Druid - Distributed, column-oriented, real-time analytics data store. (Source Code)
Apache-2.0Java/Docker - EDA - Web application for data analysis and visualization.
AGPL-3.0Nodejs/Docker - ghstats
⚠- Dashboard for tracking GitHub repos traffic history longer than 14 days.MITDocker - GoAccess - Real-time web log analyzer and interactive viewer that runs in a terminal. (Source Code)
GPL-2.0C - GoatCounter - Easy web statistics without tracking of personal data. (Source Code)
EUPL-1.2Go - Litlyx - All-in-one Analytics Solution. Setup in 30 seconds. Display all your data on an AI-powered dashboard. Fully self-hostable and GDPR compliant. (Source Code)
Apache-2.0Docker - Liwan - Privacy-first web analytics. (Demo, Source Code)
Apache-2.0Rust/Docker - Matomo - Web analytics that protects your data and your customers' privacy (alternative to Google Analytics). (Source Code)
GPL-3.0PHP - Metabase - Easy way for everyone in your company to ask questions and learn from data. (Source Code)
AGPL-3.0Java/Docker - Middleware - Tool designed to help engineering leaders measure and analyze the effectiveness of their teams using the DORA metrics. (Source Code)
Apache-2.0Docker/Python/Nodejs - Mixpost - Social media management software to easily create, schedule, publish, and manage social media content in one place (alternative to Hootsuite, Buffer, and other social media tools). (Source Code)
MITPHP/Docker - Netron - Visualizer for neural network and machine learning models. (Source Code)
MITPython/Nodejs - Offen - Fair, lightweight and open web analytics tool. Gain insights while your users have full access to their data. (Demo, Source Code)
Apache-2.0Go/Docker - Plausible Analytics - Simple, lightweight (< 1 KB) and privacy-friendly web analytics. (Source Code)
AGPL-3.0Elixir - PostHog - Product analytics, session recording, feature flagging and a/b testing that you can self-host (alternative to Mixpanel/Amplitude/Heap/HotJar/Optimizely). (Source Code)
MITPython - Postiz
⚠- Schedule posts, track the performance of your content, and manage all your social media accounts in one place (Alternative to Buffer, Hootsuite, Sprout Social). (Source Code)AGPL-3.0Docker - Prisme Analytics - Privacy-focused and progressive analytics service based on Grafana. (Source Code)
AGPL-3.0/MITDocker - Redash - Connect and query your data sources, build dashboards to visualize data and share them with your company. (Source Code)
BSD-2-ClauseDocker - RudderStack - Collect, unify, transform, and store your customer data, and route it to a wide range of common, popular marketing, sales, and product tools (alternative to Segment). (Source Code)
AGPL-3.0Docker/K8S/Go/Nodejs - Shynet - Modern, privacy-friendly, and detailed web analytics that works without cookies or JS.
Apache-2.0Python/Docker - Socioboard
⚠- Social media management, analytics, and reporting platform supporting nine social media networks out-of-the-box.GPL-3.0Nodejs - Statistics for Strava
⚠- Statistics dashboard generated from Strava data. (Demo)AGPL-3.0Docker - Superset - Modern data exploration and visualization platform. (Source Code)
Apache-2.0Python - Swetrix - Ultimate, open-source web analytics to satisfy all your needs. (Demo, Source Code)
AGPL-3.0Docker - Umami - Simple, fast, privacy-focused alternative to Google Analytics. (Demo, Source Code)
MITNodejs/Docker
- Aptabase - Privacy first and simple analytics for mobile and desktop apps. (Source Code)
-
 @ b0a838f2:34ed3f19
2025-05-23 17:43:42
@ b0a838f2:34ed3f19
2025-05-23 17:43:42Automation
- Ctfreak - IT task scheduler with mobile-friendly web UI to schedule concurrent, remote and chained execution of Bash / Powershell / SQL scripts, Webhooks, and more.
⊘ ProprietaryUnknown - CxReports
⚠- Reporting and PDF document generation with a user-friendly WYSIWYG template editor, API, automated email delivery, and robust security features.⊘ ProprietaryDocker - n8n - Free node based Workflow Automation Tool. Easily automate tasks across different services. (Source Code)
Apache-2.0/Commons-ClauseNodejs
Communication - Custom Communication Systems
- Chaskiq - Full featured live chat, help center and CRM as an alternative to Intercom & Drift, Crisp and others. (Source Code)
AGPL-3.0/Commons-ClauseRuby - Chatwoot - Customer communication platform (alternative to Intercom & Zendesk). (Source Code)
⊘ ProprietaryRuby/Docker/K8S - Groupboard - Online whiteboard, audio/video conferencing, screen sharing, shared code editing and optional session recording/playback.
⊘ ProprietaryUnknown - PrivMX WebMail - Alternative private mail system - web-based, end-to-end encrypted by design, self-hosted, decentralized, uses independent PKI. Easy to install and administrate, freeware, open-source.
⊘ ProprietaryPHP - Virola Messenger - Instant messaging and collaboration tool with private and group chat rooms, continuous voice and video meetings, files sharing, issue tracking with integrated task board. Alternative to Slack and others.
⊘ ProprietaryC++ - WorkAdventure - Virtual office / virtual conference application presented as a 16-bit RPG video game. (Demo, Source Code)
AGPL-3.0/Commons-ClauseDocker
Communication - Email - Complete Solutions
- Forward Email - Privacy-focused encrypted email for everyone. All-in-one alternative to Gmail + Mailchimp + Sendgrid. (Source Code)
BUSL-1.1/MPL-2.0Nodejs/Docker
Communication - Email - Mailing Lists and Newsletters
- Sendy - Self-hosted email newsletter application that lets you send bulk emails via Amazon Simple Email Service (SES) or other SMTP services.
⊘ ProprietaryPHP
Communication - SIP
- 3CX - Full-featured PABX system, with call queues, built-in web conferencing, live chat and social media messaging all on one system.
⊘ ProprietaryUnknown
Communication - Video Conferencing
- TrueConf - Platform for your corporate communications, based on the advanced architecture, with support for UltraHD video conferencing, built-in messenger with personal and group chats, and a free version for up to 1,000 users.
⊘ ProprietaryDocker/deb
Content Management Systems (CMS)
- CraftCMS - Content-first CMS that aims to make life enjoyable for developers and content managers alike. (Demo, Source Code)
⊘ ProprietaryPHP - Kirby - File-based CMS. Easy to setup. Easy to use. Flexible as hell. (Source Code)
⊘ ProprietaryPHP - october - CMS platform based on the Laravel PHP Framework. (Source Code)
⊘ ProprietaryPHP
Database Management
- Cluster Control - Setup many databases in few clicks with monitoring, load balancing and more.
⊘ Proprietarydeb/Ansible/Shell/Docker - Directus - An Instant App & API for your SQL Database. Directus wraps your new or existing SQL database with a realtime GraphQL+REST API for developers, and an intuitive admin app for non-technical users. (Source Code)
BUSL-1.1Nodejs/Docker - MindsDB - AI layer for existing databases that allows you to effortlessly develop, train and deploy state-of-the-art machine learning models using standard queries. (Source Code)
Elastic-2.0Docker/Python
Document Management - E-books
- Bookwyrm - Social network for tracking your reading, talking about books, writing reviews, and discovering what to read next. (Source Code)
⊘ ProprietaryPython - Ubooquity - Free to use, versatile, lightweight, multi-platform, and secure home server for your comic and e-book library.
⊘ ProprietaryJava
E-commerce
- OXID eShop - OXID eShop is a flexible open source e-commerce software with a wide range of functionalities. (Source Code)
⊘ ProprietaryPHP - Sharetribe - Open-source platform to create your own peer-to-peer marketplace, also available with SaaS model. (Source Code)
⊘ ProprietaryRuby
File Transfer & Synchronization
- FileRun - Complete solution for your files with integration with Google and Office. (Demo)
⊘ ProprietaryPHP - Resilio Sync - Proprietary peer-to-peer file synchronisation tool.
⊘ ProprietaryUnknown - Yetishare - Powerful file hosting script with support for Amazon S3, Wasabi, Backblaze, local, direct and SFTP storage. (Demo)
⊘ ProprietaryPHP
Games
- Cubiks-2048 - Clone of 2048 game in 3D. (Demo)
CC-BY-NC-4.0Javascript - untrusted - Unique puzzle game designed for geeks and developers, where you solve the puzzles in the game by reading and writing Javascript. (Demo)
CC-BY-NC-SA-3.0Nodejs
Games - Administrative Utilities & Control Panels
- GameVault - Organize, download, and play DRM-free games from your own server, complete with metadata enrichment and user-friendly interface. (Demo, Source Code)
CC-BY-NC-SA-4.0Nodejs/Docker
Knowledge Management Tools
- Wiznote - Manage your knowledge in documents with folders, markdown, full text search and webpage collection support. (Demo, Clients)
⊘ ProprietaryDocker
Maps and Global Positioning System (GPS)
- MapTiler Server - Host OpenStreetMap vector tiles, satellite imagery, own geodata and data from PostGIS database.
⊘ ProprietaryUnknown
Media Streaming - Video Streaming
- Channels DVR Server - Flexible server providing a whole home self hosted DVR experience for Channels.
⊘ ProprietaryUnknown - Emby - Home media server supporting both DLNA and DIAL (Chromecast) devices out-of-the-box.
⊘ ProprietaryC# - Plex - Centralized home media playback system with a powerful central server.
⊘ ProprietaryUnknown - Subsonic - Web-based media streamer and jukebox. (Demo)
⊘ ProprietaryUnknown
Miscellaneous
- Keygen - Software licensing and distribution API. (Source Code)
⊘ ProprietaryRuby - RemoteUtilities - Remote Utilities is self-hosted remote support software for LAN administration and remote support over the Internet.
⊘ ProprietaryUnknown - ScreenConnect - Lightning-fast remote support and remote access to connect instantly and solve problems faster.
⊘ ProprietaryUnknown
Money, Budgeting & Management
- Akaunting - Accounting software designed for small businesses and freelancers. (Source Code)
BUSL-1.1PHP - Pancake - Online invoicing, project management, time tracking and proposal software.
⊘ ProprietaryPHP
Photo Galleries
- Lomorage - Google photo alternative via simple self-hosting software. Supported clients: iOS, Android, Web, MAC/Windows. Backend can run on Raspberry pi, Armbian, MAC/Windows/Linux. (Source Code)
⊘ ProprietaryGo - PhotoStructure - All your family's photos and videos automatically organized into a fun and beautiful website. Runs via Docker, NodeJS, or native desktop installers.
⊘ ProprietaryNodejs - Reservo - Scalable image hosting script with support for CDNs, paid account upgrades, advertising spots and drag & drop upload. (Demo)
⊘ ProprietaryPHP - Single File PHP Gallery - Web gallery in one single PHP file.
⊘ ProprietaryPHP
Recipe Management
- Tandoor Recipes - Django application to manage, tag and search recipes using either built-in models or external storage providers hosting PDFs, Images or other files. (Demo, Source Code)
MIT/Commons-ClausePython/Docker/K8S
Remote Access
- SparkView - Browser-based remote access solution. No VPN client; just deploy the software in the DMZ. Access VMs, desktops, servers, and apps anytime, anywhere, without complex and costly client rollouts or user management.
⊘ ProprietaryJava
Search Engines
- ElasticSearch - Distributed, RESTful search and analytics engine. (Source Code)
SSPL-1.0Java
Self-hosting Solutions
- Axigen - Turnkey messaging solution for small & micro businesses, integration projects or test environments.
⊘ ProprietaryUnknown - Cloud Seeder - One-click server appliance deployment and maintenance suite for Windows, MacOS and Linux. (Source Code)
⊘ ProprietaryGo - Cloudron - Open-core software allowing you to effortlessly self-host web apps on your server. (Demo, Source Code)
⊘ ProprietaryNodejs/Docker - Cosmos - Run server applications securely and with built-in privacy features. It acts as a secure gateway to your application, as well as a server manager. (Source Code)
Apache-2.0/Commons-ClauseDocker/Go - Easypanel - Modern server control panel powered by Docker.
⊘ ProprietaryDocker - Poste.io - Full-featured solution for your Email server. Native implementation of last anti-SPAM methods, webmail and easy administration included. Free tier available. (Demo)
⊘ ProprietaryUnknown - Umbrel - A beautiful personal server OS for self-hosting. Install on a Raspberry Pi 4 or Ubuntu/Debian. (Source Code)
⊘ ProprietaryNodejs/Docker - Unraid
⚠- Linux-based operating system designed to run on home media server setups.⊘ ProprietaryUnknown
Software Development - API Management
- Composio
⚠- Integration platform for AI agents & LLMs with support for 250+ apps and custom tools. (Source Code)Elastic-2.0Python - Hook0 - Webhooks-as-a-service (WaaS) that makes it easy for online products to provide webhooks. Dispatch up to 3,000 events/month with 7 days of history retention for free. (Source Code)
SSPL-1.0Rust/Nodejs/Docker
Software Development - IDE & Tools
- RepoFlow - Simplify package management for npm, PyPI, Docker, Go, Helm, and more. Try it for free with 10GB storage, 10GB bandwidth, 100 packages, and unlimited users in the cloud, or self-hosted for personal use only.
⊘ ProprietaryNodejs/Docker
Software Development - Low Code
- Budibase - Build and automate internal tools, admin panels, dashboards, CRUD apps, and more, in minutes (alternative to Outsystems, Retool, Mendix, Appian). (Source Code)
⊘ ProprietaryNodejs/Docker/K8S - Dify.ai - Build, test and deploy LLM applications. (Source Code)
Apache-2.0/Commons-ClauseDocker - UI Bakery - Build internal tools, customer portals, and CRUD apps quickly. Configure scheduled jobs and webhooks. Create structure and manage data through a GUI. (Demo, Source Code)
⊘ ProprietaryDocker/K8S
Software Development - Project Management
- 92five - Self-hosted project management application.
⊘ ProprietaryPHP - Active Collab - Project management.
⊘ ProprietaryPHP - BitBucket Server - Enterprise-level Git solution (alternative to GitLab).
⊘ ProprietaryJava - Buddy Enterprise - Git and Continuous Integration/Delivery Platform.
⊘ ProprietaryNodejs/Java - Crucible - Peer code review application.
⊘ ProprietaryJava - Kanban Tool - Advanced Kanban boards with time tracking.
⊘ ProprietaryRuby - Kantree - Work management and collaboration.
⊘ ProprietaryPython - Solo - Free project management app created for freelancers. Create contacts, manage tasks, upload files, track project progress, and keep notes. (Demo)
⊘ ProprietaryPHP
Software Development - Testing
- Bamboo - Continuous integration server.
⊘ ProprietaryJava - BrowserStack Automate TurboScale - Scalable browser automation grid on your cloud (AWS, GCP and Azure) supporting Selenium and Playwright.
⊘ ProprietaryDocker - Grai - Automated integration testing. Uses data lineage to statically analyze the impact of a data change across your entire data stack. (Source Code)
Elastic-2.0Docker - Moon - Efficient Selenium protocol implementation running everything in Kubernetes or Openshift.
⊘ ProprietaryGo - Sentry Self-Hosted - Powerful error tracking platform with wide language support and a robust API. (Source Code)
BUSL-1.1Python/Django
Ticketing
- Bugsink - Real-time error tracking for your applications with all the details in one place. Easy setup with clear instructions included. (Source Code)
⊘ ProprietaryPython/Docker - Deskpro - On-Premise help desk software that includes email, chat, voice & help centre publishing. Full visible source code and API.
⊘ ProprietaryUnknown - Erxes - Marketing, sales, and customer service platform designed to help businesses attract more engaged customers. (Source Code)
AGPL-3.0/Commons-ClauseDocker/Nodejs - Full Help - Simple, easy to use help desk & knowledge base software. Custom branding, custom themes, restful API, communication channels, multi-company support, multi-language support, and much more! At least 1 new release per month.
⊘ ProprietaryPHP - JIRA - Professional and extensible issue tracker.
⊘ ProprietaryJava - Jitbit Helpdesk - Help desk software - simple but powerful. (Demo)
⊘ Proprietary.NET - SupportPal - Powerful help desk software - easy, fast and intuitive. (Demo)
⊘ ProprietaryPHP
Time Tracking
- Virtual TimeClock - Powerful, easy-to-use time tracking software. (Demo)
⊘ ProprietaryUnknown
Wikis
- Outline
⚠- Extensible wiki for your team. (Source Code)BUSL-1.1Nodejs/Docker
- Ctfreak - IT task scheduler with mobile-friendly web UI to schedule concurrent, remote and chained execution of Bash / Powershell / SQL scripts, Webhooks, and more.
-
 @ 91bea5cd:1df4451c
2025-05-23 17:04:49
@ 91bea5cd:1df4451c
2025-05-23 17:04:49Em nota, a prefeitura justificou que essas alterações visam ampliar a segurança das praias, conforto e organização, para os frequentadores e trabalhadores dos locais. No entanto, Orla Rio, concessionária responsável pelos espaços, e o SindRio, sindicato de bares e restaurantes, ficou insatisfeita com as medidas e reforçou que a música ao vivo aumenta em mais de 10% o ticket médio dos estabelecimentos e contribui para manter os empregos, especialmente na baixa temporada.
De acordo com Paes, as medidas visam impedir práticas ilegais para que a orla carioca continue sendo um espaço ativo econômico da cidade: “Certas práticas são inaceitáveis, especialmente por quem tem autorização municipal. Vamos ser mais restritivos e duros. A orla é de todos”.
Saiba quais serão as 16 proibições nas praias do Rio de Janeiro
- Utilização de caixas de som, instrumentos musicais, grupos ou qualquer equipamento sonoro, em qualquer horário. Apenas eventos autorizados terão permissão.
- Venda ou distribuição de bebidas em garrafas de vidro em qualquer ponto da areia ou do calçadão.
- Estruturas comerciais ambulantes sem autorização, como carrocinhas, trailers, food trucks e barracas.
- Comércio ambulante sem permissão, incluindo alimentos em palitos, churrasqueiras, isopores ou bandejas térmicas improvisadas.
- Circulação de ciclomotores e patinetes motorizados no calçadão.
- Escolinhas de esportes ou recreações não autorizadas pelo poder público municipal.
- Ocupação de área pública com estruturas fixas ou móveis de grandes proporções sem autorização.
- Instalação de acampamentos improvisados em qualquer trecho da orla.
- Práticas de comércio abusivo ou enganosas, incluindo abordagens insistentes. Quiosques e barracas devem exibir cardápio, preços e taxas de forma clara.
- Uso de animais para entretenimento, transporte ou comércio.
- Hasteamento ou exibição de bandeiras em mastros ou suportes.
- Fixação de objetos ou amarras em árvores ou vegetação.
- Cercadinhos feitos por ambulantes ou quiosques, que impeçam a livre circulação de pessoas.
- Permanência de carrinhos de transporte de mercadorias ou equipamentos fora dos momentos de carga e descarga.
- Armazenamento de produtos, barracas ou equipamentos enterrados na areia ou depositados na vegetação de restinga.
- Uso de nomes, marcas, logotipos ou slogans em barracas. Apenas a numeração sequencial da prefeitura será permitida.
-
 @ 5144fe88:9587d5af
2025-05-23 17:01:37
@ 5144fe88:9587d5af
2025-05-23 17:01:37The recent anomalies in the financial market and the frequent occurrence of world trade wars and hot wars have caused the world's political and economic landscape to fluctuate violently. It always feels like the financial crisis is getting closer and closer.
This is a systematic analysis of the possibility of the current global financial crisis by Manus based on Ray Dalio's latest views, US and Japanese economic and financial data, Buffett's investment behavior, and historical financial crises.
Research shows that the current financial system has many preconditions for a crisis, especially debt levels, market valuations, and investor behavior, which show obvious crisis signals. The probability of a financial crisis in the short term (within 6-12 months) is 30%-40%,
in the medium term (within 1-2 years) is 50%-60%,
in the long term (within 2-3 years) is 60%-70%.
Japan's role as the world's largest holder of overseas assets and the largest creditor of the United States is particularly critical. The sharp appreciation of the yen may be a signal of the return of global safe-haven funds, which will become an important precursor to the outbreak of a financial crisis.
Potential conditions for triggering a financial crisis Conditions that have been met 1. High debt levels: The debt-to-GDP ratio of the United States and Japan has reached a record high. 2. Market overvaluation: The ratio of stock market to GDP hits a record high 3. Abnormal investor behavior: Buffett's cash holdings hit a record high, with net selling for 10 consecutive quarters 4. Monetary policy shift: Japan ends negative interest rates, and the Fed ends the rate hike cycle 5. Market concentration is too high: a few technology stocks dominate market performance
Potential trigger points 1. The Bank of Japan further tightens monetary policy, leading to a sharp appreciation of the yen and the return of overseas funds 2. The US debt crisis worsens, and the proportion of interest expenses continues to rise to unsustainable levels 3. The bursting of the technology bubble leads to a collapse in market confidence 4. The trade war further escalates, disrupting global supply chains and economic growth 5. Japan, as the largest creditor of the United States, reduces its holdings of US debt, causing US debt yields to soar
Analysis of the similarities and differences between the current economic environment and the historical financial crisis Debt level comparison Current debt situation • US government debt to GDP ratio: 124.0% (December 2024) • Japanese government debt to GDP ratio: 216.2% (December 2024), historical high 225.8% (March 2021) • US total debt: 36.21 trillion US dollars (May 2025) • Japanese debt/GDP ratio: more than 250%-263% (Japanese Prime Minister’s statement)
Before the 2008 financial crisis • US government debt to GDP ratio: about 64% (2007) • Japanese government debt to GDP ratio: about 175% (2007)
Before the Internet bubble in 2000 • US government debt to GDP ratio: about 55% (1999) • Japanese government debt to GDP ratio: about 130% (1999)
Key differences • The current US debt-to-GDP ratio is nearly twice that before the 2008 crisis • The current Japanese debt-to-GDP ratio is more than 1.2 times that before the 2008 crisis • Global debt levels are generally higher than historical pre-crisis levels • US interest payments are expected to devour 30% of fiscal revenue (Moody's warning)
Monetary policy and interest rate environment
Current situation • US 10-year Treasury yield: about 4.6% (May 2025) • Bank of Japan policy: end negative interest rates and start a rate hike cycle • Bank of Japan's holdings of government bonds: 52%, plans to reduce purchases to 3 trillion yen per month by January-March 2026 • Fed policy: end the rate hike cycle and prepare to cut interest rates
Before the 2008 financial crisis • US 10-year Treasury yield: about 4.5%-5% (2007) • Fed policy: continuous rate hikes from 2004 to 2006, and rate cuts began in 2007 • Bank of Japan policy: maintain ultra-low interest rates
Key differences • Current US interest rates are similar to those before the 2008 crisis, but debt levels are much higher than then • Japan is in the early stages of ending its loose monetary policy, unlike before historical crises • The size of global central bank balance sheets is far greater than at any time in history
Market valuations and investor behavior Current situation • The ratio of stock market value to the size of the US economy: a record high • Buffett's cash holdings: $347 billion (28% of assets), a record high • Market concentration: US stock growth mainly relies on a few technology giants • Investor sentiment: Technology stocks are enthusiastic, but institutional investors are beginning to be cautious
Before the 2008 financial crisis • Buffett's cash holdings: 25% of assets (2005) • Market concentration: Financial and real estate-related stocks performed strongly • Investor sentiment: The real estate market was overheated and subprime products were widely popular
Before the 2000 Internet bubble • Buffett's cash holdings: increased from 1% to 13% (1998) • Market concentration: Internet stocks were extremely highly valued • Investor sentiment: Tech stocks are in a frenzy
Key differences • Buffett's current cash holdings exceed any pre-crisis level in history • Market valuation indicators have reached a record high, exceeding the levels before the 2000 bubble and the 2008 crisis • The current market concentration is higher than any period in history, and a few technology stocks dominate market performance
Safe-haven fund flows and international relations Current situation • The status of the yen: As a safe-haven currency, the appreciation of the yen may indicate a rise in global risk aversion • Trade relations: The United States has imposed tariffs on Japan, which is expected to reduce Japan's GDP growth by 0.3 percentage points in fiscal 2025 • International debt: Japan is one of the largest creditors of the United States
Before historical crises • Before the 2008 crisis: International capital flows to US real estate and financial products • Before the 2000 bubble: International capital flows to US technology stocks
Key differences • Current trade frictions have intensified and the trend of globalization has weakened • Japan's role as the world's largest holder of overseas assets has become more prominent • International debt dependence is higher than any period in history
-
 @ da8b7de1:c0164aee
2025-05-23 16:08:53
@ da8b7de1:c0164aee
2025-05-23 16:08:53Amerikai Nukleáris Fordulat és Pénzügyi hatások
Donald Trump elnök bejelentette, hogy végrehajtási rendeleteket ír alá a nukleáris energia fellendítésére . Ezek célja az új reaktorok engedélyezési folyamatának egyszerűsítése, az üzemanyag-ellátási láncok megerősítése, valamint a hazai ipar támogatása az orosz és kínai nyersanyagfüggőség csökkentése érdekében. A hír hatására az amerikai és globális nukleáris részvények jelentős emelkedést mutattak: az Uránium Energy 11%, a Centrus Energy 19,6%, az Oklo 16%, a Nano Nuclear 15%, a Nu Power 14,1%, a Global X Uranium ETF pedig 9%-kal erősödött . A növekvő energiaigény, különösen a mesterséges intelligencia által hajtott adatközpontok miatt, tovább növeli a nukleáris energia stratégiai szerepét az USA-ban .
Európai és Nemzetközi Nukleáris Fejlemények
Svédország parlamentje elfogadta az új állami támogatási keretrendszert, amely akár 5 000 MW új nukleáris kapacitás beruházását ösztönzi . Az intézkedés célja az áramárak stabilizálása, az ellátásbiztonság növelése és a zöld átmenet támogatása. A program keveri az állami hiteleket és a piaci árgaranciákat (CfD), a projektek finanszírozásában pedig a magántőke is részt vesz. A törvény 2025. augusztus 1-jén lép hatályba, a végrehajtás azonban még EU-jóváhagyásra vár .
Nukleáris Ellátási Lánc és Iparági Konferencia
Május 20–21-én Varsóban rendezték meg az első World Nuclear Supply Chain Conference-t, amelynek célja a globális nukleáris ellátási lánc megerősítése és bővítése . A konferencián elhangzottak szerint az iparág előtt álló kihívás a kapacitás gyors növelése, hiszen a cél a globális nukleáris kapacitás megháromszorozása 2050-ig. A World Nuclear Association legfrissebb elemzése szerint a következő 15 évben akár 2 billió dollár értékű beruházási lehetőség nyílhat a nemzetközi ellátási láncban . A rendezvényen kiemelték az innováció, a lokalizáció és az iparági együttműködés fontosságát, valamint a szállítási és geopolitikai kihívásokat is.
Új Projektek, Technológiai és Piaci Hírek
Az Egyesült Államokban a Tennessee Valley Authority (TVA) benyújtotta az első hivatalos engedélykérelmet egy BWRX-300 típusú kis moduláris reaktor (SMR) építésére a Clinch River telephelyen . Indiában a nukleáris hatóság jóváhagyta a Mahi Banswara Rajasthan Atomerőmű négy új blokkjának helyszínét . Kínában befejeződött a Haiyang 3 atomerőmű gőzturbinájának fő egységeinek telepítése . Belgiumban és Dániában is újraértékelik a nukleáris energia szerepét, míg Brazília Oroszországgal közös SMR-projektet tervez .
Iparági Trendek és Kilátások
A World Nuclear Association és az International Energy Agency (IEA) szerint a globális nukleáris energiatermelés 2025-ben minden korábbinál magasabb szintet érhet el, köszönhetően az új reaktorok üzembe helyezésének és a stabil, alacsony kibocsátású energiaforrások iránti növekvő igénynek . A nukleáris üzemanyag-ellátási lánc megerősítése, az uránbányászat, az átalakítás és a dúsítás bővítése, valamint a szállítási kapacitás fejlesztése mind kulcsfontosságú tényezők lesznek a következő években .
Hivatkozások
reuters.com
investopedia.com
nucnet.org
world-nuclear-news.org
world-nuclear.org -
 @ 90152b7f:04e57401
2025-05-23 15:48:58
@ 90152b7f:04e57401
2025-05-23 15:48:58U.S. troops would enforce peace under Army study
The Washington Times - September 10, 2001
by Rowan Scarborough
https://www.ord.io/70787305 (image) https://www.ord.io/74522515 (text)
An elite U.S. Army study center has devised a plan for enforcing a major Israeli-Palestinian peace accord that would require about 20,000 well-armed troops stationed throughout Israel and a newly created Palestinian state. There are no plans by the Bush administration to put American soldiers into the Middle East to police an agreement forged by the longtime warring parties. In fact, Defense Secretary Donald H. Rumsfeld is searching for ways to reduce U.S. peacekeeping efforts abroad, rather than increasing such missions. But a 68-page paper by the Army School of Advanced Military Studies (SAMS) does provide a look at the daunting task any international peacekeeping force would face if the United Nations authorized it, and Israel and the Palestinians ever reached a peace agreement.
Located at Fort Leavenworth, Kan., the School for Advanced Military Studies is both a training ground and a think tank for some of the Army’s brightest officers. Officials say the Army chief of staff, and sometimes the Joint Chiefs of Staff, ask SAMS to develop contingency plans for future military operations. During the 1991 Persian Gulf war, SAMS personnel helped plan the coalition ground attack that avoided a strike up the middle of Iraqi positions and instead executed a “left hook” that routed the enemy in 100 hours.
The cover page for the recent SAMS project said it was done for the Joint Chiefs of Staff. But Maj. Chris Garver, a Fort Leavenworth spokesman, said the study was not requested by Washington. “This was just an academic exercise,” said Maj. Garver. “They were trying to take a current situation and get some training out of it.” The exercise was done by 60 officers dubbed “Jedi Knights,” as all second-year SAMS students are nicknamed.
The SAMS paper attempts to predict events in the first year of a peace-enforcement operation, and sees possible dangers for U.S. troops from both sides. It calls Israel’s armed forces a “500-pound gorilla in Israel. Well armed and trained. Operates in both Gaza . Known to disregard international law to accomplish mission. Very unlikely to fire on American forces. Fratricide a concern especially in air space management.”
Of the Mossad, the Israeli intelligence service, the SAMS officers say: “Wildcard. Ruthless and cunning. Has capability to target U.S. forces and make it look like a Palestinian/Arab act.”
On the Palestinian side, the paper describes their youth as “loose cannons; under no control, sometimes violent.” The study lists five Arab terrorist groups that could target American troops for assassination and hostage-taking. The study recommends “neutrality in word and deed” as one way to protect U.S. soldiers from any attack. It also says Syria, Egypt and Jordan must be warned “we will act decisively in response to external attack.”
It is unlikely either of the three would mount an attack. Of Syria’s military, the report says: “Syrian army quantitatively larger than Israeli Defense Forces, but largely seen as qualitatively inferior. More likely, however, Syrians would provide financial and political support to the Palestinians, as well as increase covert support to terrorism acts through Lebanon.” Of Egypt’s military, the paper says, “Egyptians also maintain a large army but have little to gain by attacking Israel.”
The plan does not specify a full order of battle. An Army source who reviewed the SAMS work said each of a possible three brigades would require about 100 Bradley fighting vehicles, 25 tanks, 12 self-propelled howitzers, Apache attack helicopters, Kiowa Warrior reconnaissance helicopters and Predator spy drones. The report predicts that nonlethal weapons would be used to quell unrest. U.S. European Command, which is headed by NATO’s supreme allied commander, would oversee the peacekeeping operation. Commanders would maintain areas of operation, or AOs, around Nablus, Jerusalem, Hebron and the Gaza strip. The study sets out a list of goals for U.S. troops to accomplish in the first 30 days. They include: “create conditions for development of Palestinian State and security of “; ensure “equal distribution of contract value or equivalent aid” that would help legitimize the peacekeeping force and stimulate economic growth; “promote U.S. investment in Palestine”; “encourage reconciliation between entities based on acceptance of new national identities”; and “build lasting relationship based on new legal borders and not religious-territorial claims.”
Maj. Garver said the officers who completed the exercise will hold major planning jobs once they graduate. “There is an application process” for students, he said. “They screen their records, and there are several tests they go through before they are accepted by the program. The bright planners of the future come out of this program.”
James Phillips, a Middle East analyst at the Heritage Foundation, said it would be a mistake to put peacekeepers in Israel, given the “poor record of previous monitors.” “In general, the Bush administration policy is to discourage a large American presence,” he said. “But it has been rumored that one of the possibilities might be an expanded CIA role.” “It would be a very different environment than Bosnia,” said Mr. Phillips, referring to America’s six-year peacekeeping role in Bosnia-Herzegovina. “The Palestinian Authority is pushing for this as part of its strategy to internationalize the conflict. Bring in the Europeans and Russia and China. But such monitors or peacekeeping forces are not going to be able to bring peace. Only a decision by the Palestinians to stop the violence and restart talks could possibly do that.”
<<https://www.ord.io/70787305>>
<<<https://www.ord.io/74522515>>>
-
 @ 87e98bb6:8d6616f4
2025-05-23 15:36:32
@ 87e98bb6:8d6616f4
2025-05-23 15:36:32Use this guide if you want to keep your NixOS on the stable branch, but enable unstable application packages. It took me a while to figure out how to do this, so I wanted to share because it ended up being far easier than most of the vague explanations online made it seem.
I put a sample configuration.nix file at the very bottom to help it make more sense for new users. Remember to keep a backup of your config file, just in case!
If there are any errors please let me know. I am currently running NixOS 24.11.
Steps listed in this guide: 1. Add the unstable channel to NixOS as a secondary channel. 2. Edit the configuration.nix to enable unstable applications. 3. Add "unstable." in front of the application names in the config file (example: unstable.program). This enables the install of unstable versions during the build. 4. Rebuild.
Step 1:
- Open the console. (If you want to see which channels you currently have, type: sudo nix-channel --list)
- Add the unstable channel, type: sudo nix-channel --add https://channels.nixos.org/nixpkgs-unstable unstable
- To update the channels (bring in the possible apps), type: sudo nix-channel --update
More info here: https://nixos.wiki/wiki/Nix_channels
Step 2:
Edit your configuration.nix and add the following around your current config:
``` { config, pkgs, lib, ... }:
let unstable = import
{ config = { allowUnfree = true; }; }; in { #insert normal configuration text here } #remember to close the bracket!```
At this point it would be good to save your config and try a rebuild to make sure there are no errors. If you have errors, make sure your brackets are in the right places and/or not missing. This step will make for less troubleshooting later on if something happens to be in the wrong spot!
Step 3:
Add "unstable." to the start of each application you want to use the unstable version. (Example: unstable.brave)
Step 4:
Rebuild your config, type: sudo nixos-rebuild switch
Example configuration.nix file:
```
Config file for NixOS
{ config, pkgs, lib, ... }:
Enable unstable apps from Nix repository.
let unstable = import
{ config = { allowUnfree = true; }; }; in { #Put your normal config entries here in between the tags. Below is what your applications list needs to look like.
environment.systemPackages = with pkgs; [ appimage-run blender unstable.brave #Just add unstable. before the application name to enable the unstable version. chirp discord ];
} # Don't forget to close bracket at the end of the config file!
``` That should be all. Hope it helps.
-
 @ 10f7c7f7:f5683da9
2025-05-23 15:26:17
@ 10f7c7f7:f5683da9
2025-05-23 15:26:17While I’m going to stand by what I said in my previous piece, minimise capital gains payments, don’t fund the government, get a loan against your bitcoin, but the wheels in my left curve brain have continued to turn, well that, and a few more of my 40PW insights. I mentioned about paying attention to the risks involved in terms of borrowing against your bitcoin, and hopefully ending up paying less in bitcoin at the end of the loan, even if you ultimately sold bitcoin to pay off the loan. However, the idea of losing control of the bitcoin I have spent a good deal of time and effort accumulating being out of my control has led me to reconsider. I also realised I didn’t fully flesh out some other topics that I think are relevant, not least time preference, specifically in relation to what you’re buying. The idea of realising a lump some of capital to live your dreams, buy a house or a cool car may be important, but it may be worth taking a step back and looking at what you’re purchasing. Are you only purchasing those things because you had been able to get this new money “tax free”? If that is the case, and the fiat is burning a hold in your pocket, maybe you’ve just found yourself with the same fiat brained mentality you have been working so hard to escape from while you have sacrificed and saved to stack sats.
While it may no longer be necessary to ask yourself whether a particular product or service is worth selling your bitcoin for because you’ve taken out a loan, it may still be worth asking yourself whether a particular loan fuelled purchase is worth forfeiting control of your keys for? Unlike the foolish 18 year-old, released into a world with their newly preapproved credit card, you need to take a moment and ask yourself:
Is the risk worth it?
Is the purchase worth it?
But also take a moment to consider a number of other things, are there fiat options?
Where in the cycle might you be?
Or if I’m thinking carefully about this, will whatever I’m buying hold its value (experiences may be more difficult to run the numbers on)?
The reason for asking these things, is that if you still have a foot in the fiat world, dealing with a fiat bank account, fiat institutions may still be very willing to provide you with a loan at a lower rate than a bitcoin backed loan. Particularly if you’re planning on using that money to buy a house; if you can qualify for a mortgage, get a mortgage, but if you need cash for a deposit, maybe that is where the bitcoin backed loan may come in. Then, it may be worth thinking about where are you in the bitcoin cycle? No one can answer this, but with the historic data we have, it appears logical that after some type of run up, prices may retrace (Dan Held’s supercycle withstanding).
Matteo Pellegrini with Daniel Prince provided a new perspective on this for me. Rather the riding the bull market gains all the way through to the bear market bottom, what happens if I chose to buy an asset that didn’t lose quite as much fiat value as bitcoin, for example, a Swiss Watch, or a tasteful, more mature sports car? If that was the purchase of choice, they suggested that you could enjoy the car, “the experience” for a year or two, then realise the four door estate was likely always the better option, sell it and be able to buy back as many, if not slightly more bitcoin that you originally sold (not financial, classic car or price prediction advice, I’m not accredited to advise pretty much anything). Having said that, it is a scenario I think worth thinking about when the bitcoin denominated dream car begins to make financial sense.
Then, as we begin to look forward to the near inevitable bear market (they are good for both stacking and grinding), if we’ve decided to take out a loan rather than sell, we then may ultimately need to increase our collateral to maintain loan to value requirements, as well as sell more bitcoin to cover repayments (if that’s the route we’re taking). This then moves us back into the domain of saying, well in actual fact we should just sell our bitcoin when we can get most dollar for it (or the coolest car), with a little extra to cover future taxes, it is probably better to sell near a top than a bottom. The balance between these two rather extreme positions could be to take out a fiat loan to buy the item and maybe sell sufficient bitcoin so you’re able to cover the loan for a period of time (less taxable events to keep track of and also deals with future uncertainty of bitcoin price). In this case, if the loan timeframe is longer than the amount of loan your sale can cover, by the time you need to sell anymore, the price should have recovered from a cycle bottom.
In this scenario, apart from the smaller portion of bitcoin you have had to sell, the majority of your stack can remain in cold storage, the loan you took out will be unsecured (particularly against your bitcoin), but even if it isn’t, the value of what you purchase maintains its value, you can in theory exit the loan at any point by selling the luxury item. Then within this scenario, if you had sold near a top, realised the car gave you a bad back or made you realise you staying humble is more important, sold it, paid off the loan, there may even be a chance you could buy back more bitcoin with the money you had left over from selling your bitcoin to fund the loan.
I have no idea of this could actually work, but to be honest, I’m looking forward to trying it out in the next 6-12 months, although I may keep my daily driver outside of my bitcoin strategy (kids still need a taxi service). Having said that, I think there are some important points to consider in addition to not paying capital gains tax (legally), as well as the opportunities of bitcoin loans. They are still very young products and to quote every trad-fi news outlet, “bitcoin is still a volatile asset”, these thought experiments are still worth working through. To push back on the Uber fiat journalist, Katie Martin, “Bitcoin has no obvious use case”, it does, it can be a store of value to hold or sell, it can be liquid and flexible collateral, but also an asset that moves independently of other assets to balance against fiat liabilities. The idea of being able to release some capital, enjoy the benefits of the capital for a period, before returning that capital to store value feels like a compelling one.
The important thing to remember is that there are a variety of options, whether selling for cash, taking out a bitcoin backed loan, taking out a fiat loan or some combination of each. Saying that, what I would think remains an important question to ask irrespective of the option you go for:
Is what I’m planning on buying, worth selling bitcoin for?
If it cannot pass this first question, maybe it isn’t worth purchasing to start with.
-
 @ 0e9491aa:ef2adadf
2025-05-23 14:01:33
@ 0e9491aa:ef2adadf
2025-05-23 14:01:33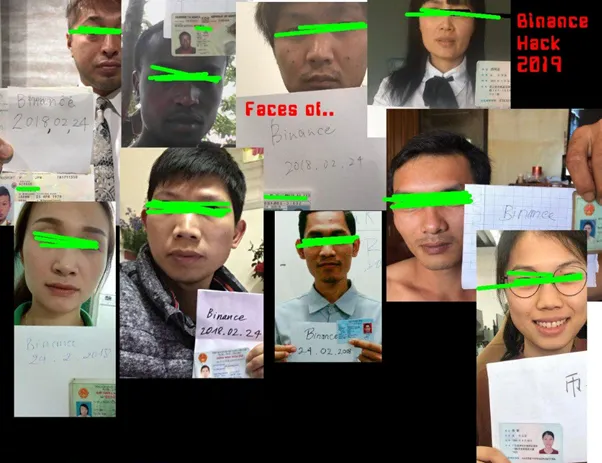
What is KYC/AML?
- The acronym stands for Know Your Customer / Anti Money Laundering.
- In practice it stands for the surveillance measures companies are often compelled to take against their customers by financial regulators.
- Methods differ but often include: Passport Scans, Driver License Uploads, Social Security Numbers, Home Address, Phone Number, Face Scans.
- Bitcoin companies will also store all withdrawal and deposit addresses which can then be used to track bitcoin transactions on the bitcoin block chain.
- This data is then stored and shared. Regulations often require companies to hold this information for a set number of years but in practice users should assume this data will be held indefinitely. Data is often stored insecurely, which results in frequent hacks and leaks.
- KYC/AML data collection puts all honest users at risk of theft, extortion, and persecution while being ineffective at stopping crime. Criminals often use counterfeit, bought, or stolen credentials to get around the requirements. Criminals can buy "verified" accounts for as little as $200. Furthermore, billions of people are excluded from financial services as a result of KYC/AML requirements.
During the early days of bitcoin most services did not require this sensitive user data, but as adoption increased so did the surveillance measures. At this point, most large bitcoin companies are collecting and storing massive lists of bitcoiners, our sensitive personal information, and our transaction history.
Lists of Bitcoiners
KYC/AML policies are a direct attack on bitcoiners. Lists of bitcoiners and our transaction history will inevitably be used against us.
Once you are on a list with your bitcoin transaction history that record will always exist. Generally speaking, tracking bitcoin is based on probability analysis of ownership change. Surveillance firms use various heuristics to determine if you are sending bitcoin to yourself or if ownership is actually changing hands. You can obtain better privacy going forward by using collaborative transactions such as coinjoin to break this probability analysis.
Fortunately, you can buy bitcoin without providing intimate personal information. Tools such as peach, hodlhodl, robosats, azteco and bisq help; mining is also a solid option: anyone can plug a miner into power and internet and earn bitcoin by mining privately.
You can also earn bitcoin by providing goods and/or services that can be purchased with bitcoin. Long term, circular economies will mitigate this threat: most people will not buy bitcoin - they will earn bitcoin - most people will not sell bitcoin - they will spend bitcoin.
There is no such thing as KYC or No KYC bitcoin, there are bitcoiners on lists and those that are not on lists.
If you found this post helpful support my work with bitcoin.

-
 @ eed7ca5d:191de8eb
2025-05-23 13:58:46
@ eed7ca5d:191de8eb
2025-05-23 13:58:46Growing up, we were told that in order to build wealth, we need to save little by little. By living below your means, you are providing more for your future.
It is a simple formula that will help you build up the capital necessary to buy a car, a house or start a business… You prioritize long-term benefits and delayed gratification over immediate rewards.
This is called having a low-time preference. In contrast, high-time preference individuals prioritize today over tomorrow, seeking immediate gratification.
Austrian economists explain that civilization growth is driven by low-time preference societies. Groups of individuals who prioritize long-term planning are able to innovate and develop new tools for a better future. Over time, this behavior leads to technological inventions like the light bulb and artistic masterpieces like the Notre Dame cathedral.
***What happens when you realize that the money you save is losing value over time? ***
There is less incentive to save for the future, because in the future your savings will be worth less. You might as well spend it now and enjoy life today.
When the money you save loses its value, you are facing one of two choices:
-
Spend it today and reap the rewards of your hard work;
-
Invest it (stocks, real estate, etc.) with the hope to reap higher rewards later, bearing the risk of losing it all if the investment does not pay off.
There is a distinct difference between saving and investing as the latter approach is riskier than the former. By investing, you are betting on the upside while bearing the downside risk. Saving, in contrast, comes without downside risk. That difference becomes blurry when the money you save is losing value. In fact, saving becomes inherently a losing approach. Logically, you will be forced to place a speculative bet with the hope to outperform the guaranteed loss of value. You are required to find a way to hedge your bet…
Humans over time have always sought out a medium to save their economic energy for a better future. That used to be beads and seashells, and evolved to precious metals like gold and silver.
Money is a tool that we use to save our economic energy over time, and exchange value with each other.
I spend time fishing, you spend time farming, the neighbor spends time building homes, and society rewards us with money for the time and energy we spent being productive
Today, the tool that we use to save our economic energy is clearly losing value over time. The nominal value remains the same, but the purchasing power is decreasing. In other words, the value of our time today will be worth less in the future.
That explains why everyone around us is looking for the next best investment opportunity. We are all needing to become investment experts, speculators, on top of our respective professions. Speculation became necessary, and some of us are forced into a high-time preference lifestyle.
Earn now and spend it all now before you lose it.
This should not be the case…
Time is Money
Our time is the only scarce resource we all have. We use it to be productive and generate economic value, then store that value in the form of money in order to reap the rewards in the future.
Money is the abstract representation of our time. Hence, time is money.
In January 2009, at the height of the global financial crisis, a software protocol called Bitcoin was released pseudonymously by Satoshi Nakamoto. This individual (or group) released a whitepaper a few months prior named “Bitcoin: A Peer-to-Peer Electronic Cash System” outlining how the system enables secure, peer-to-peer transactions without relying on a central authority. (https://bitcoin.org/bitcoin.pdf)
Although there are more technical concepts involved, the bitcoin protocol can be thought of as a language for communicating value. The same way we respect the rules of the English language to communicate ideas with one another, bitcoin users adhere to the network’s consensus rules to communicate value with each other in a peer-to-peer fashion.
There are no physical or digital coins in the bitcoin network. Rather, it is a collection of transactions transferring value from sender to recipient. Transactions are validated and propagated by nodes across the network, before being recorded into the blockchain. The Bitcoin blockchain is a global public ledger of all transactions that cannot be altered.
More importantly, Bitcoin is money that does not lose value overtime.
-
Its supply is capped at 21 million coins.
-
Its scarcity increases over time due to the predictable issuance rate, which halves roughly every 4 years.
-
Its decentralized nature puts the power in the hands of its users.
-
There is no governing body that can devalue or alter it.
It is a tool that we can use to save our economic energy over time, and be able to use it later.
It is the scarcest verifiable commodity: we cannot make more of it no matter how high its demand grows. That cannot be said for any other commodity in the world today.
A savings tool in disguise
See, most people tend to view bitcoin as another speculative investment. They presume they have missed out on another investment opportunity, and it’s now too late to get in.
Meanwhile, it is quite the opposite. Bitcoin’s value will keep growing over time due to its deflationary nature.
With bitcoin, we can save for a better future, for a rainy day, and spend more time with our loved ones or focusing on our craft to build better tools or artistic masterpieces. It takes away the burden of having to speculate on which stock will perform best, or which real estate market will grow the fastest, all while working one or multiple jobs
Bitcoin is not another investment opportunity you missed out on. It is the best savings tool humans have invented (or discovered), while everything else is the speculative bet. Bitcoin is the hedge against the guaranteed devaluation of money, without any counterparty risk.
What we were taught as children is true. With the right tool, the idea that saving will help you build wealth overtime stands true. Bitcoin might seem like an investment today given the volatility during its adoption phase. In reality, it is the perfect way to store your time and economic energy and grow your wealth. Whether you make $1/hour or $1M/hour, you can start saving in the best money humans have invented.
My goal is to help people around me understand this technology and break the stigma around it.
Bitcoin is not the next best investment.
It is the best tool we have found to store our economic energy across time and exchange value with each other.
Bitcoin is Money.
-
-
 @ 348e7eb2:3b0b9790
2025-05-23 15:15:45
@ 348e7eb2:3b0b9790
2025-05-23 15:15:45Nostr-Konto erstellen - funktioniert
Was der Button macht
Der folgende Code fügt einen Button hinzu, der per Klick einen Nostr-Anmeldedialog öffnet. Alle Schritte sind im Code selbst ausführlich kommentiert.
Erläuterungen:
- Dynamisches Nachladen: Das Script
modal.jswird nur bei Klick nachgeladen, um Fehlermeldungen beim Initial-Load zu vermeiden. -
Parameter im Überblick:
-
baseUrl: Quelle für API und Assets. an: App-Name für den Modal-Header.aa: Farbakzent ( als Hex).al: Sprache des Interfaces.am: Licht- oder Dunkelmodus.s: Empfohlene Nostr-Accountsafb/asb: Bunker-Modi für erhöhten Datenschutz.aan/aac: Steuerung der Rückgabe privater Schlüssel.arr/awr: Primal Relay als Lese- und Schreib-Relay.- Callbacks:
onComplete: Schließt das Modal, zeigt eine Bestätigung und bietet die Weiterleitung zu Primal an.onCancel: Schließt das Modal und protokolliert den Abbruch.
Damit ist der gesamte Code sichtbar, kommentiert und erklärt.
- Dynamisches Nachladen: Das Script
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-23 13:46:21
@ 5d4b6c8d:8a1c1ee3
2025-05-23 13:46:21You'd think I'd be most excited to talk about that awesome Pacers game, but, no. What I'm most excited about this week is that @grayruby wants to continue Beefing with Cowherd.
Still, I am excited to talk about Tyrese Haliburton becoming a legendary Knicks antagonist. Unfortunately, the Western Conference Finals are not as exciting. Also, why was the MVP announcement so dumb?
The T20k cricket contest is tightening up, as we head towards the finish. Can @Coinsreporter hold on to his vanishing lead?
@Carresan has launched Football Madness. Let's see if we understand whatever the hell this is any better than we did last week.
On this week's Blok'd Shots, we'll ridicule Canada for their disgraceful loss in the World Championships and talk about the very dominant American Florida Panthers, who are favorites to win the Stanley Cup.
Are the Colorado the worst team in MLB history?
The Tush Push has survived another season. Will the NFL eventually ban it or will teams adjust?
Plus, whatever else Stackers want to talk about.
https://stacker.news/items/987399
-
 @ 0e9491aa:ef2adadf
2025-05-23 15:01:52
@ 0e9491aa:ef2adadf
2025-05-23 15:01:52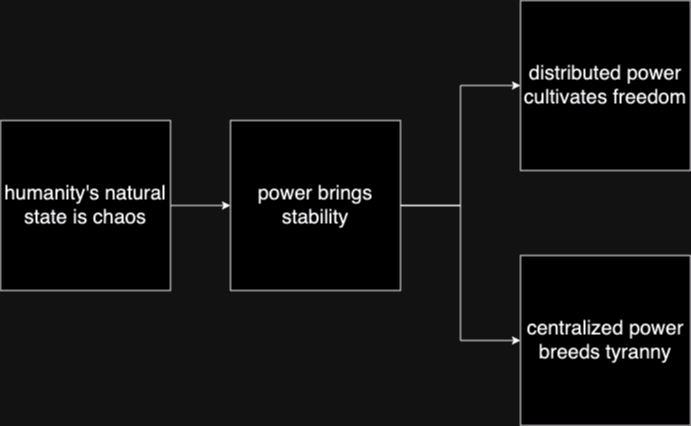
Humanity's Natural State Is Chaos
Without order there is chaos. Humans competing with each other for scarce resources naturally leads to conflict until one group achieves significant power and instates a "monopoly on violence."Power Brings Stability
Power has always been the key means to achieve stability in societies. Centralized power can be incredibly effective in addressing issues such as crime, poverty, and social unrest efficiently. Unfortunately this power is often abused and corrupted.Centralized Power Breeds Tyranny
Centralized power often leads to tyrannical rule. When a select few individuals hold control over a society, they tend to become corrupted. Centralized power structures often lack accountability and transparency, and rely too heavily on trust.Distributed Power Cultivates Freedom
New technology that empowers individuals provide us the ability to rebuild societies from the bottom up. Strong individuals that can defend and provide for themselves will help build strong local communities on a similar foundation. The result is power being distributed throughout society rather than held by a select few.In the short term, relying on trust and centralized power is an easy answer to mitigating chaos, but freedom tech tools provide us the ability to build on top of much stronger distributed foundations that provide stability while also cultivating individual freedom.
The solution starts with us. Empower yourself. Empower others. A grassroots freedom tech movement scaling one person at a time.
If you found this post helpful support my work with bitcoin.

-
 @ 450102fc:539757ac
2025-05-23 13:43:58
@ 450102fc:539757ac
2025-05-23 13:43:58With Nostr, Jack is well ahead of what Elon and Zuck have learned about censorship
Mark Zuckerberg’s announcement that he is dropping censorship in the U.S. for Facebook and Instagram was accompanied by a comment that he is going to work with the U.S. government to encourage other countries to not censor content. Upon acquiring Twitter, Elon Musk dropped censorship and soon learned that government mandates from across the world censor content.
In 2024, Brazil blocked Twitter until it complied with censorship demands, France arrested Telegram’s CEO Pavel Durov, the EU censored additional Russian outlets and wrote letters to Twitter mandating more content moderation, and Australia announced it will fine platforms for misinformation.
The current U.S. administration had a heavy censorship hand and had threatened to revoke Section 230 which protects Internet sites from liability about their users’ content. Zuck indicated in his announcement and a letter to Congress in November that Meta felt coerced to comply. Twitter under Jack Dorsey was also coerced to censor, as disclosed in the Twitter Files and Alex Berenson’s amended censorship lawsuit with new insider materials from Twitter.
Western governments did not typically engage in government guidance or mandates on content until after the Brexit and Trump elections in 2016 followed by the Russia-Ukraine war in 2022. Once Western governments realized that they had lost narrative control, they started playing catch up with China, which was well aware from the start of the power of social networks to both disrupt and control narratives.
Due to the secretive nature of government guidance and mandates, Elon and those outside social media organizations had only witnessed basic content moderation. Jack and Zuck had already experienced years of coercive government guidance threatening Section 230 revocation as well as numerous explicit censorship mandates from Western governments.
Zuck’s response was to downrank and de-emphasize political content in early 2021 after the bruising 2020 U.S. election cycle. This was a difficult decision since Facebook made a lot of money from political arguments, as I pointed out in a 2019 article for VentureBeat. Zuck sidestepped government pressure and continued to grow his properties. Correspondingly, despite the volumes of racist and homophobic content on Instagram, there is not much pressure for content moderation from groups like Media Matters and GARM that have targeted X/Twitter.
Jack’s response was to fund Bluesky to shift Twitter to an open protocol like email’s SMTP and the web’s HTTP. Governments can of course censor at the protocol level with firewalls like they currently do for email and web, but by separating the application and protocol layers, Jack recognized that social networks could operate like any other Internet infrastructure that is content neutral. Jack departed Bluesky when the company started massively moderating accounts and content. Jack then discovered Nostr (Notes and Other Stuff Transmitted by Relays), a decentralized messaging protocol initially created by an anonymous developer FiatJeff, much like an anonymous developer Satoshi Nakamoto created Bitcoin.
Nostr is reminiscent of FidoNet, a popular store-and-forward messaging protocol for Bulletin Board Systems (BBS) in the 1980s. Each BBS was fully independent, and each could choose which forum messages to store-and-forward, whether to moderate content, and how long to keep the messages. In addition, FidoNet could store-and-forward private messages between users. UseNet also operated in a similar store-and-forward manner for Internet forums, but did not operate private messages since the Internet already had SMTP.
Nostr developers offer an active ecosystem of both clients and servers offering an interface familiar to social network users, as well as micro apps offering new functionality on top of the protocol. Nostr is decentralized with no central control point and transmits messages across independently operated relays. Just like with current email systems and Nostr predecessors FidoNet and UseNet the independence of the relays create inefficiency. Different users may not see each others’ replies chronologically until the messages transmission has caught up, and not all relays transmit all messages. FidoNet and UseNet were inefficient due to resource constraints such as long distance charges and intermittent connectivity. Nostr and Bitcoin use inefficiency to engineer resilience into the protocol.
A Nostr account can never be “revoked,” however relays are not obligated to carry an account’s messages. Users can easily switch relays or even operate their own. As part of the new generation of decentralized crypto software, Nostr uses a public/private key combination for identity, and you can optionally publish your profile name, e-mail address, and lightning wallet associated with the key. Nostr clients sign messages with your private key when you post, and users know it’s you by your public key. A note of caution: just like with crypto, if your private key gets compromised or lost, it’s like losing or having your Bitcoin private key stolen.
A new administration could easily coerce social media companies. This time, Elon stood in the face of a government onslaught. Zuck followed when the coast was clear. Jack has laid the foundation for the future. https://npub1g5qs9.layer3.press/articles/cd5020b0-08ad-409d-b792-81387bb4f060
-
 @ 348e7eb2:3b0b9790
2025-05-23 14:27:03
@ 348e7eb2:3b0b9790
2025-05-23 14:27:03Nostr-Konto erstellen
Was der Button macht
Der folgende Code fügt einen Button hinzu, der per Klick einen Nostr-Anmeldedialog öffnet. Alle Schritte sind im Code selbst ausführlich kommentiert.
```html
```
Erläuterungen:
- Dynamisches Nachladen: Das Script
modal.jswird nur bei Klick nachgeladen, um Fehlermeldungen beim Initial-Load zu vermeiden. -
Parameter im Überblick:
-
baseUrl: Quelle für API und Assets. an: App-Name für den Modal-Header.aa: Farbakzent (Foerbico-Farbe als Hex).al: Sprache des Interfaces.am: Licht- oder Dunkelmodus.afb/asb: Bunker-Modi für erhöhten Datenschutz.aan/aac: Steuerung der Rückgabe privater Schlüssel.arr/awr: Primal Relay als Lese- und Schreib-Relay.-
Callbacks:
-
onComplete: Schließt das Modal, zeigt eine Bestätigung und bietet die Weiterleitung zu Primal an. onCancel: Schließt das Modal und protokolliert den Abbruch.
Damit ist der gesamte Code sichtbar, kommentiert und erklärt.
Accounts
as: [ 'npub1f7jar3qnu269uyx5p0e4v24hqxjnxysxudvujza2ur5ehltvdeqsly2fx9', 'npub1ak7mtjnyha96rjqjdaav7tkjjulcmx7vgmcd6map82vsags8dhtsmecgtd', 'npub1cmvrxn8k50ljamtqlcd3eqznqlnz50zpyp2q45dh0p5gcvyg84ksxezqps', 'npub14c3ffunyuzpl69y526dcknn785t35zvq6y63pvxvmfvghfj6dewqc0v55d', ],
## funzt#️⃣ https://nstart.me/de?an=MeineApp&at=popup&am=light&aa=203a8f&asb=yes&s=npub1f7jar3qnu269uyx5p0e4v24hqxjnxysxudvujza2ur5ehltvdeqsly2fx9,npub1ak7mtjnyha96rjqjdaav7tkjjulcmx7vgmcd6map82vsags8dhtsmecgtd - Dynamisches Nachladen: Das Script
-
 @ d12614be:8ed99bc6
2025-05-23 13:35:09
@ d12614be:8ed99bc6
2025-05-23 13:35:09Test article 23.05.2025 2
https://drewdru.layer3.press/articles/ddd70871-69c2-41af-ae56-13fea76050e0
-
 @ 0e9491aa:ef2adadf
2025-05-23 14:01:32
@ 0e9491aa:ef2adadf
2025-05-23 14:01:32
The former seems to have found solid product market fit. Expect significant volume, adoption, and usage going forward.
The latter's future remains to be seen. Dependence on Tor, which has had massive reliability issues, and lack of strong privacy guarantees put it at risk.
— ODELL (@ODELL) October 27, 2022
The Basics
- Lightning is a protocol that enables cheap and fast native bitcoin transactions.
- At the core of the protocol is the ability for bitcoin users to create a payment channel with another user.
- These payment channels enable users to make many bitcoin transactions between each other with only two on-chain bitcoin transactions: the channel open transaction and the channel close transaction.
- Essentially lightning is a protocol for interoperable batched bitcoin transactions.
- It is expected that on chain bitcoin transaction fees will increase with adoption and the ability to easily batch transactions will save users significant money.
- As these lightning transactions are processed, liquidity flows from one side of a channel to the other side, on chain transactions are signed by both parties but not broadcasted to update this balance.
- Lightning is designed to be trust minimized, either party in a payment channel can close the channel at any time and their bitcoin will be settled on chain without trusting the other party.
There is no 'Lightning Network'
- Many people refer to the aggregate of all lightning channels as 'The Lightning Network' but this is a false premise.
- There are many lightning channels between many different users and funds can flow across interconnected channels as long as there is a route through peers.
- If a lightning transaction requires multiple hops it will flow through multiple interconnected channels, adjusting the balance of all channels along the route, and paying lightning transaction fees that are set by each node on the route.
Example: You have a channel with Bob. Bob has a channel with Charlie. You can pay Charlie through your channel with Bob and Bob's channel with User C.
- As a result, it is not guaranteed that every lightning user can pay every other lightning user, they must have a route of interconnected channels between sender and receiver.
Lightning in Practice
- Lightning has already found product market fit and usage as an interconnected payment protocol between large professional custodians.
- They are able to easily manage channels and liquidity between each other without trust using this interoperable protocol.
- Lightning payments between large custodians are fast and easy. End users do not have to run their own node or manage their channels and liquidity. These payments rarely fail due to professional management of custodial nodes.
- The tradeoff is one inherent to custodians and other trusted third parties. Custodial wallets can steal funds and compromise user privacy.
Sovereign Lightning
- Trusted third parties are security holes.
- Users must run their own node and manage their own channels in order to use lightning without trusting a third party. This remains the single largest friction point for sovereign lightning usage: the mental burden of actively running a lightning node and associated liquidity management.
- Bitcoin development prioritizes node accessibility so cost to self host your own node is low but if a node is run at home or office, Tor or a VPN is recommended to mask your IP address: otherwise it is visible to the entire network and represents a privacy risk.
- This privacy risk is heightened due to the potential for certain governments to go after sovereign lightning users and compel them to shutdown their nodes. If their IP Address is exposed they are easier to target.
- Fortunately the tools to run and manage nodes continue to get easier but it is important to understand that this will always be a friction point when compared to custodial services.
The Potential Fracture of Lightning
- Any lightning user can choose which users are allowed to open channels with them.
- One potential is that professional custodians only peer with other professional custodians.
- We already see nodes like those run by CashApp only have channels open with other regulated counterparties. This could be due to performance goals, liability reduction, or regulatory pressure.
- Fortunately some of their peers are connected to non-regulated parties so payments to and from sovereign lightning users are still successfully processed by CashApp but this may not always be the case going forward.
Summary
- Many people refer to the aggregate of all lightning channels as 'The Lightning Network' but this is a false premise. There is no singular 'Lightning Network' but rather many payment channels between distinct peers, some connected with each other and some not.
- Lightning as an interoperable payment protocol between professional custodians seems to have found solid product market fit. Expect significant volume, adoption, and usage going forward.
- Lightning as a robust sovereign payment protocol has yet to be battle tested. Heavy reliance on Tor, which has had massive reliability issues, the friction of active liquidity management, significant on chain fee burden for small amounts, interactivity constraints on mobile, and lack of strong privacy guarantees put it at risk.
If you have never used lightning before, use this guide to get started on your phone.
If you found this post helpful support my work with bitcoin.

-
 @ a296b972:e5a7a2e8
2025-05-23 12:42:10
@ a296b972:e5a7a2e8
2025-05-23 12:42:10Was Rudolf Steiner vor gut 110 Jahren an Informationen zusammengetragen und kommentiert hat, liest sich in großen Abschnitten so, als ob es in der heutigen Zeit geschrieben worden wäre. Man trifft auf eine ganze Reihe von „guten, alten Bekannten“, die auch heute noch maßgeblich an den Strippen ziehen. Deutlich wird, dass ein Krieg nicht aus heiterem Himmel ausbricht, sondern das im Vorfeld schon Kräfte wirken, die auf einen Krieg hinarbeiten. Wie jetzt wieder im Ukraine-Krieg wird diese Vorgeschichte gerne versucht unter den Teppich zu kehren und hochkompetente, sauber recherchierende, akribisch Quellen angebende Journalisten, wie z. B. Frau Gabriele Krone-Schmalz oder Herr Patrik Baab, der sich auf eigene Kosten einen Eindruck von vor Ort verschafft hat, werden versucht mundtot zu machen und mittlerweile gar nicht mehr zu Gesprächen im öffentlich-rechtlichen Rundfunk eingeladen, weil sie die fortlaufende Gehirnwäsche des Ministeriums für Wahrheit und Narrative mit ihren Aussagen gefährden. Andere kommen auf die Sanktionsliste.
Auch heute ist von den „Guten“ und den „Bösen“ die Rede, was darauf schließen lässt, dass man durchaus eingesteht, dass hier geistige Kräfte am Werk sind. Rudolf Steiner kommt auf diese immer wieder zu sprechen. Aus der von ihm gegebenen anthroposophischen Geisteswissenschaft heraus, beleuchtet er die Vorgänge innerhalb der gesamten Menschheitsentwicklung. Mancher stört sich hier an Begriffen, die man heute so nicht mehr verwenden würde. Dabei ist immer zu berücksichtigen, zu welcher Zeit die Vorträge gehalten wurden. Die Anthroposophie von Rudolf Steiner gilt heute bei vielen auch als „umstritten“, aber was ist das heute nicht? Fast könnte man es schon als Auszeichnung sehen, wenn etwas „umstritten“ ist, denn das ist mittlerweile ein Beweis dafür, dass es Ansichten, Meinungen und Einschätzungen gibt, die in einer gesunden Demokratie innerhalb einer Kontroverse zu einem Dialog und Austausch beitragen können, der jedoch leider derzeit weder gewünscht ist, noch gepflegt wird, was an der „Spaltung“ deutlich zu sehen ist. Und auch unter den Anthroposophen hat die „Spaltung“ Einzug gehalten.
Um das aktuelle, viele Bereiche umschließende, gigantische Lügenkonstrukt aufrecht zu erhalten, ist mittlerweile jedes Mittel recht, von der Deutungshoheit der Wahrheit durch systemkonforme Begutachter, bis hin zu infantil-kleingeistigen Kindergartenspielchen, um gegenläufige Meinungen oder Oppositionelle in ihrem Wirken zu behindern.
Der gesunde Hausverstand wird ausgetrocknet, und der Garten des Wahnsinns wird durch immer neue Ideen kranker Geister weiter gegossen, gehegt und gepflegt.
Die Zeitgeschichtlichen Betrachtungen von Rudolf Steiner bestehen aus 3 Bänden aus der GA (Gesamtausgabe):
GA 173 a – Wege zu einer objektiven Urteilsbildung
GA 173 b – Das Karma der Unwahrhaftigkeit
GA 173 c – Die Wirklichkeit okkulter Impulse
Sie bestehen aus niedergeschriebenen Vorträgen und einem sehr umfangreichen Anhang mit näheren Erläuterungen und einer Schilderung der Entstehung dieser drei Bände.
Es bedarf einiger Eingewöhnung in die zur damaligen Zeit verwendete Sprache Rudolf Steiners, der ein Meister im Bilden von Schachtelsätzen war. Der Inhalt jedoch, und auf den kommt es ja an, berührt immer wieder den in allen Menschen vorhandenen Wahrheitssinn.
Hier nur eine kleine Kostprobe, die vielleicht das Interesse wecken kann, sich mit diesem derzeit besonders aktuellen Werk näher zu beschäftigen.
GA 173a, 6. Vortrag, Seite 205 und Seite 206, Dornach, 17. Dezember 1916:
„Viel intimer, viel verborgener liegen die Dinge bei der englischen Politik, die ja ganz beeinflußt ist von dem, was in solcher Weise hinter ihr steckt. Da handelt es sich darum, daß man die Wege findet, um die entsprechenden Menschen an die richtigen Plätze zu befördern. Okkultistische Menschen, im Hintergrunde stehend, sind oftmals – na, verzeihen Sie – Einser, bloße Einser, und bedeuten für sich nichts Besonderes; sie brauchen noch etwas anderes – sie brauchen Nullen. Nullen sind ja nicht Einser, aber (fügt man eine Null zu einer Eins), dann wird gleich eine Zehn daraus. Und wenn man noch mehr Nullen hinzufügt – jede Null ist nur eine Null, aber wenn die Eins irgendwo steckt, dann ist gar mancherlei da, zum Beispiel die Tausend, und wenn man die Eins zudeckt, dann sind (scheinbar) nur die Nullen da; die Nullen brauchen aber nur in der entsprechenden Weise mit den Einsern kombiniert zu sein, und sie brauchen nicht einmal viel zu wissen von der Art, wie sie mit den Einsern kombiniert sind.“
Schildert diese 108 Jahre alte Beschreibung nicht genau das, was sich heute vor unseren Augen abspielt?
Dieser Artikel wurde mit dem Pareto-Client geschrieben
* *
(Bild von pixabay)
-
 @ 1c5ff3ca:efe9c0f6
2025-05-23 10:13:57
@ 1c5ff3ca:efe9c0f6
2025-05-23 10:13:57Auto-Deployment on a VPS with GitHub Actions
Introduction
This tutorial describes how you can deploy an application on a VPS using GitHub Actions. This way, changes in your GitHub repository are automatically deployed to your VPS.
Prerequisites
- GitHub Account
- GitHub Repository
- Server + SSH access to the server
Step 1 - SSH Login to Server
Open a terminal and log in via SSH. Then navigate to the
.sshdirectoryssh user@hostname cd ~/.sshStep 2 - Create an SSH Key
Now create a new SSH key that we will use for auto-deployment. In the following dialog, simply press "Enter" repeatedly until the key is created.
ssh-keygen -t ed25519 -C "service-name-deploy-github"Step 3 - Add the Key to the
authorized_keysFilecat id_ed25519.pub >> authorized_keys(If you named the key file differently, change this accordingly)
Step 4 - GitHub Secrets
In order for the GitHub Action to perform the deployment later, some secrets must be stored in the repository. Open the repository on GitHub. Navigate to "Settings" -> "Secrets And Variables" -> "Actions". Add the following variables:
HOST: Hostname or IP address of the serverUSERNAME: Username you use to log in via SSHSSHKEY: The private key (copy the content fromcat ~/.ssh/id_ed25519)PORT: 22
Step 5 - Create the GitHub Action
Now create the GitHub Action for auto-deployment. The following GitHub Action will be used: https://github.com/appleboy/scp-action In your local repository, create the file
.github/workflows/deploy.yml:```yaml name: Deploy on: [push] jobs: build: runs-on: ubuntu-latest steps: - uses: actions/checkout@v1 - name: Copy repository content via scp uses: appleboy/scp-action@master with: host: ${{ secrets.HOST }} username: ${{ secrets.USERNAME }} port: ${{ secrets.PORT }} key: ${{ secrets.SSHKEY }} source: "." target: "/your-target-directory"
- name: Executing a remote command uses: appleboy/ssh-action@master with: host: ${{ secrets.HOST }} username: ${{ secrets.USERNAME }} port: ${{ secrets.PORT }} key: ${{ secrets.SSHKEY }} script: | ls```
This action copies the repository files to your server using
scp. Afterwards, thelscommand is executed. Here you can add appropriate commands that rebuild your service or similar. To rebuild and start a docker service you could use something like this or similar:docker compose -f target-dir/docker-compose.yml up --build -dNow commit this file and in the "Actions" tab of your repository, the newly created action should now be visible and executed. With every future change, the git repository will now be automatically copied to your server.Sources
I read this when trying out, but it did not work and I adapted the
deploy.ymlfile: https://dev.to/knowbee/how-to-setup-continuous-deployment-of-a-website-on-a-vps-using-github-actions-54im -
 @ 0e9491aa:ef2adadf
2025-05-23 14:01:32
@ 0e9491aa:ef2adadf
2025-05-23 14:01:32
Bank run on every crypto bank then bank run on every "real" bank.
— ODELL (@ODELL) December 14, 2022
The four main banks of bitcoin and “crypto” are Signature, Prime Trust, Silvergate, and Silicon Valley Bank. Prime Trust does not custody funds themselves but rather maintains deposit accounts at BMO Harris Bank, Cross River, Lexicon Bank, MVB Bank, and Signature Bank. Silvergate and Silicon Valley Bank have already stopped withdrawals. More banks will go down before the chaos stops. None of them have sufficient reserves to meet withdrawals.
Bitcoin gives us all the ability to opt out of a system that has massive layers of counterparty risk built in, years of cheap money and broken incentives have layered risk on top of risk throughout the entire global economy. If you thought the FTX bank run was painful to watch, I have bad news for you: every major bank in the world is fractional reserve. Bitcoin held in self custody is unique in its lack of counterparty risk, as global market chaos unwinds this will become much more obvious.
The rules of bitcoin are extremely hard to change by design. Anyone can access the network directly without a trusted third party by using their own node. Owning more bitcoin does not give you more control over the network with all participants on equal footing.
Bitcoin is:
- money that is not controlled by a company or government
- money that can be spent or saved without permission
- money that is provably scarce and should increase in purchasing power with adoptionBitcoin is money without trust. Whether you are a nation state, corporation, or an individual, you can use bitcoin to spend or save without permission. Social media will accelerate the already deteriorating trust in our institutions and as this trust continues to crumble the value of trust minimized money will become obvious. As adoption increases so should the purchasing power of bitcoin.
A quick note on "stablecoins," such as USDC - it is important to remember that they rely on trusted custodians. They have the same risk as funds held directly in bank accounts with additional counterparty risk on top. The trusted custodians can be pressured by gov, exit scam, or caught up in fraud. Funds can and will be frozen at will. This is a distinctly different trust model than bitcoin, which is a native bearer token that does not rely on any centralized entity or custodian.
Most bitcoin exchanges have exposure to these failing banks. Expect more chaos and confusion as this all unwinds. Withdraw any bitcoin to your own wallet ASAP.
Simple Self Custody Guide: https://werunbtc.com/muun
More Secure Cold Storage Guide: https://werunbtc.com/coldcard
If you found this post helpful support my work with bitcoin.

-
 @ dfc7c785:4c3c6174
2025-05-23 09:42:37
@ dfc7c785:4c3c6174
2025-05-23 09:42:37Where do I even start? Sometimes it's best to just begin writing whatever comes into your head. What do I do for a living? It used to be easy to explain, I write JavaScript, I build front-end code, in order to build apps. I am more than that though. Over the past eight years, I moved from writing Angular, to React and then to Vue. However my background was originally in writing full-stack projects, using technologies such as .NET and PHP. The thing is - the various jobs I've had recently have pigeon-holed me as front-end developer but nowadays I am starting to feel distracted by a multitude of other interesting, pivotal technologies both in my "day job" and across my wider experience as a Technologist; a phrase I prefer to use in order to describe who I am, more gernerally.
I have used untype.app to write this today, it looks great.
More to come...
-
 @ 5c26ee8b:a4d229aa
2025-05-23 08:47:45
@ 5c26ee8b:a4d229aa
2025-05-23 08:47:45Generally mentioning God, Allah, by reciting/reading the Quran or performing Salat (compulsory prayer), for instance, brings tranquility to the heart of the believer. The Salat, other than being the first deed a Muslim would be questioned about on Judgement Day, it keeps the person away from the forbidden wrong deeds too. The Salat is sufficient for obtaining God’s provision as he decrees the means for it to reach the person. Wasting or missing performing the Salat or mentioning God (Allah) by reciting/reading the Quran or Tasbieh, can lead to following the desires only and a depressed life as well as punishment in the Thereafter.
13:28 Ar-Ra'd
الَّذِينَ آمَنُوا وَتَطْمَئِنُّ قُلُوبُهُمْ بِذِكْرِ اللَّهِ ۗ أَلَا بِذِكْرِ اللَّهِ تَطْمَئِنُّ الْقُلُوبُ
Those who have believed and whose hearts are assured (tranquillised) by the remembrance of Allah. Unquestionably, by the remembrance of Allah hearts are assured (tranquillised)."
29:45 Al-Ankaboot
اتْلُ مَا أُوحِيَ إِلَيْكَ مِنَ الْكِتَابِ وَأَقِمِ الصَّلَاةَ ۖ إِنَّ الصَّلَاةَ تَنْهَىٰ عَنِ الْفَحْشَاءِ وَالْمُنْكَرِ ۗ وَلَذِكْرُ اللَّهِ أَكْبَرُ ۗ وَاللَّهُ يَعْلَمُ مَا تَصْنَعُونَ
Recite, [O Muhammad], what has been revealed to you of the Book and establish prayer. Indeed, prayer prohibits immorality and wrongdoing, and the remembrance of Allah is greater. And Allah knows that which you do.
11:114 Hud
وَأَقِمِ الصَّلَاةَ طَرَفَيِ النَّهَارِ وَزُلَفًا مِنَ اللَّيْلِ ۚ إِنَّ الْحَسَنَاتِ يُذْهِبْنَ السَّيِّئَاتِ ۚ ذَٰلِكَ ذِكْرَىٰ لِلذَّاكِرِينَ
And establish prayer at the two ends of the day and at the approach of the night. Indeed, good deeds do away with misdeeds. That is a reminder for those who remember.
20:132 Taa-Haa
وَأْمُرْ أَهْلَكَ بِالصَّلَاةِ وَاصْطَبِرْ عَلَيْهَا ۖ لَا نَسْأَلُكَ رِزْقًا ۖ نَحْنُ نَرْزُقُكَ ۗ وَالْعَاقِبَةُ لِلتَّقْوَىٰ
And enjoin prayer upon your family [and people] and be steadfast therein. We ask you not for provision; We provide for you, and the [best] outcome is for [those of] righteousness.
20:124 Taa-Haa
وَمَنْ أَعْرَضَ عَنْ ذِكْرِي فَإِنَّ لَهُ مَعِيشَةً ضَنْكًا وَنَحْشُرُهُ يَوْمَ الْقِيَامَةِ أَعْمَىٰ
And whoever turns away from My remembrance - indeed, he will have a depressed life, and We will gather him on the Day of Resurrection blind."
20:125 Taa-Haa
قَالَ رَبِّ لِمَ حَشَرْتَنِي أَعْمَىٰ وَقَدْ كُنْتُ بَصِيرًا
He will say, "My Lord, why have you raised me blind while I was [once] seeing?"
20:126 Taa-Haa
قَالَ كَذَٰلِكَ أَتَتْكَ آيَاتُنَا فَنَسِيتَهَا ۖ وَكَذَٰلِكَ الْيَوْمَ تُنْسَىٰ
[Allah] will say, "Thus did Our signs come to you, and you forgot them; and thus will you this Day be forgotten."
20:127 Taa-Haa
وَكَذَٰلِكَ نَجْزِي مَنْ أَسْرَفَ وَلَمْ يُؤْمِنْ بِآيَاتِ رَبِّهِ ۚ وَلَعَذَابُ الْآخِرَةِ أَشَدُّ وَأَبْقَىٰ
And thus do We recompense he who transgressed and did not believe in the signs of his Lord. And the punishment of the Hereafter is more severe and more enduring.
20:128 Taa-Haa
أَفَلَمْ يَهْدِ لَهُمْ كَمْ أَهْلَكْنَا قَبْلَهُمْ مِنَ الْقُرُونِ يَمْشُونَ فِي مَسَاكِنِهِمْ ۗ إِنَّ فِي ذَٰلِكَ لَآيَاتٍ لِأُولِي النُّهَىٰ
Then, has it not become clear to them how many generations We destroyed before them as they walk among their dwellings? Indeed in that are signs for those of intelligence.
49:17 Al-Hujuraat
يَمُنُّونَ عَلَيْكَ أَنْ أَسْلَمُوا ۖ قُلْ لَا تَمُنُّوا عَلَيَّ إِسْلَامَكُمْ ۖ بَلِ اللَّهُ يَمُنُّ عَلَيْكُمْ أَنْ هَدَاكُمْ لِلْإِيمَانِ إِنْ كُنْتُمْ صَادِقِينَ
They consider it a favor to you that they have accepted Islam. Say, "Do not consider your Islam a favor to me. Rather, Allah has conferred favor upon you that He has guided you to the faith, if you should be truthful."
53:29 An-Najm
فَأَعْرِضْ عَنْ مَنْ تَوَلَّىٰ عَنْ ذِكْرِنَا وَلَمْ يُرِدْ إِلَّا الْحَيَاةَ الدُّنْيَا
So turn away from whoever turns his back on Our message and desires not except the worldly life.
53:30 An-Najm
ذَٰلِكَ مَبْلَغُهُمْ مِنَ الْعِلْمِ ۚ إِنَّ رَبَّكَ هُوَ أَعْلَمُ بِمَنْ ضَلَّ عَنْ سَبِيلِهِ وَهُوَ أَعْلَمُ بِمَنِ اهْتَدَىٰ
That is their sum of knowledge. Indeed, your Lord is most knowing of who strays from His way, and He is most knowing of who is guided.
53:62 An-Najm
فَاسْجُدُوا لِلَّهِ وَاعْبُدُوا ۩
So prostrate to Allah and worship [Him].
-
 @ 0e9491aa:ef2adadf
2025-05-23 14:01:32
@ 0e9491aa:ef2adadf
2025-05-23 14:01:32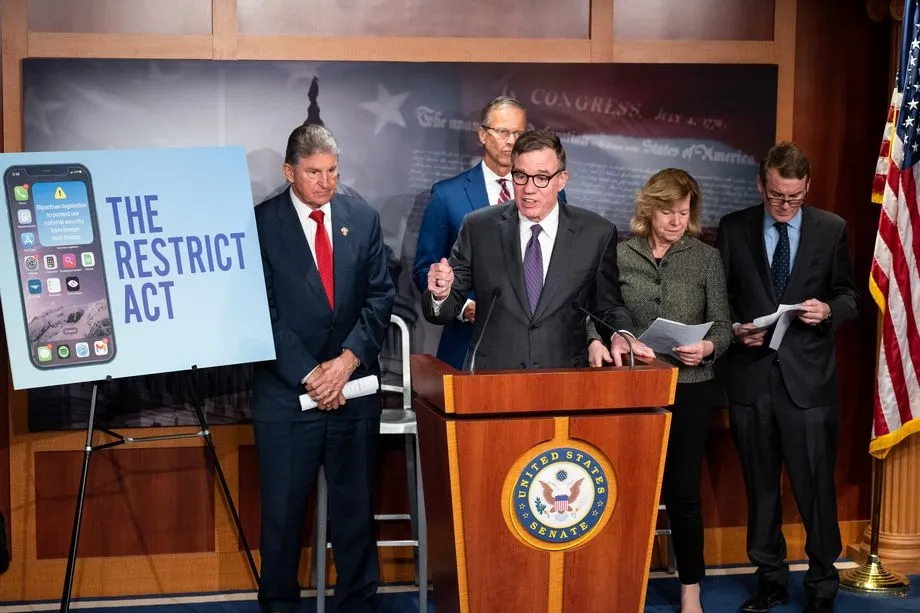
The newly proposed RESTRICT ACT - is being advertised as a TikTok Ban, but is much broader than that, carries a $1M Fine and up to 20 years in prison️! It is unconstitutional and would create massive legal restrictions on the open source movement and free speech throughout the internet.
The Bill was proposed by: Senator Warner, Senator Thune, Senator Baldwin, Senator Fischer, Senator Manchin, Senator Moran, Senator Bennet, Senator Sullivan, Senator Gillibrand, Senator Collins, Senator Heinrich, and Senator Romney. It has broad support across Senators of both parties.
Corrupt politicians will not protect us. They are part of the problem. We must build, support, and learn how to use censorship resistant tools in order to defend our natural rights.
The RESTRICT Act, introduced by Senators Warner and Thune, aims to block or disrupt transactions and financial holdings involving foreign adversaries that pose risks to national security. Although the primary targets of this legislation are companies like Tik-Tok, the language of the bill could potentially be used to block or disrupt cryptocurrency transactions and, in extreme cases, block Americans’ access to open source tools or protocols like Bitcoin.
The Act creates a redundant regime paralleling OFAC without clear justification, it significantly limits the ability for injured parties to challenge actions raising due process concerns, and unlike OFAC it lacks any carve-out for protected speech. COINCENTER ON THE RESTRICT ACT
If you found this post helpful support my work with bitcoin.

-
 @ 0e9491aa:ef2adadf
2025-05-23 14:01:32
@ 0e9491aa:ef2adadf
2025-05-23 14:01:32
@matt_odell don't you even dare not ask about nostr!
— Kukks (Andrew Camilleri) (@MrKukks) May 18, 2021
Nostr first hit my radar spring 2021: created by fellow bitcoiner and friend, fiatjaf, and released to the world as free open source software. I was fortunate to be able to host a conversation with him on Citadel Dispatch in those early days, capturing that moment in history forever. Since then, the protocol has seen explosive viral organic growth as individuals around the world have contributed their time and energy to build out the protocol and the surrounding ecosystem due to the clear need for better communication tools.
nostr is to twitter as bitcoin is to paypal
As an intro to nostr, let us start with a metaphor:
twitter is paypal - a centralized platform plagued by censorship but has the benefit of established network effects
nostr is bitcoin - an open protocol that is censorship resistant and robust but requires an organic adoption phase
Nostr is an open communication protocol that can be used to send messages across a distributed set of relays in a censorship resistant and robust way.
- Anyone can run a relay.
- Anyone can interact with the protocol.
- Relays can choose which messages they want to relay.
- Users are identified by a simple public private key pair that they can generate themselves.Nostr is often compared to twitter since there are nostr clients that emulate twitter functionality and user interface but that is merely one application of the protocol. Nostr is so much more than a mere twitter competitor. Nostr clients and relays can transmit a wide variety of data and clients can choose how to display that information to users. The result is a revolution in communication with implications that are difficult for any of us to truly comprehend.
Similar to bitcoin, nostr is an open and permissionless protocol. No person, company, or government controls it. Anyone can iterate and build on top of nostr without permission. Together, bitcoin and nostr are incredibly complementary freedom tech tools: censorship resistant, permissionless, robust, and interoperable - money and speech protected by code and incentives, not laws.
As censorship throughout the world continues to escalate, freedom tech provides hope for individuals around the world who refuse to accept the status quo. This movement will succeed on the shoulders of those who choose to stand up and contribute. We will build our own path. A brighter path.
My Nostr Public Key: npub1qny3tkh0acurzla8x3zy4nhrjz5zd8l9sy9jys09umwng00manysew95gx
If you found this post helpful support my work with bitcoin.

-
 @ 975e4ad5:8d4847ce
2025-05-23 08:47:08
@ 975e4ad5:8d4847ce
2025-05-23 08:47:08Bitcoin Is Not Just an Asset
When Satoshi Nakamoto introduced Bitcoin in 2009, the vision was clear: a decentralized currency for everyday transactions, from buying coffee to paying bills. It was designed to bypass banks and governments, empowering individuals with financial freedom. But when Bitcoin is treated as “digital gold” and locked away in wallets, it fails to fulfill this vision. Instead of replacing fiat currencies, it becomes just another investment, leaving people reliant on dollars, euros, or other traditional currencies for their daily needs.
The Problem with HODLing and Loans
Some Bitcoin enthusiasts advocate holding their coins indefinitely and taking loans against them rather than spending. This approach may seem financially savvy—Bitcoin’s value often rises over time, and loans provide liquidity without selling. But this prioritizes personal gain over the broader goal of financial revolution. Someone who holds Bitcoin while spending fiat isn’t supporting Bitcoin’s mission; they’re merely using it to stay wealthy within the existing system. This undermines the dream of a decentralized financial future.
Lightning Network: Fast and Cheap Transactions
One common argument against using Bitcoin for daily purchases is the high fees and slow transaction times on the main blockchain. Enter the Lightning Network, a second-layer solution that enables near-instant transactions with minimal fees. Imagine paying for groceries or ordering a pizza with Bitcoin, quickly and cheaply. This technology makes Bitcoin practical for everyday use, paving the way for widespread adoption.
Why Using Bitcoin Matters
If Bitcoin is only hoarded and not spent, it will remain a niche asset that shields against inflation but doesn’t challenge the fiat system. For Bitcoin to become a true alternative currency, it must be used everywhere—in stores, online platforms, and peer-to-peer exchanges. The more people and businesses accept Bitcoin, the closer we get to a world where decentralized currency is the norm. This isn’t just an investment; it’s a movement for financial freedom.\ \ Bitcoin wasn’t created to sit idly in wallets or serve as collateral for loans. It’s a tool for change that demands active use. If we want a world where individuals control their finances, we must start using Bitcoin—not just to avoid poverty, but to build a new financial reality.
-
 @ 662f9bff:8960f6b2
2025-05-23 07:38:51
@ 662f9bff:8960f6b2
2025-05-23 07:38:51I have been really busy this week with work - albeit back in Madeira - so I had little time to read or do much other than work. In the coming weeks I should have more time - I am taking a few weeks off work and have quite a list of things to do.
First thing is to relax a bit and enjoy the pleasant weather here in Funchal for a few days. With 1st May tomorrow it does seem that there will be quite a bit to do..
Some food for thought for you. Who takes and makes your decisions? Do you make them yourself based on information that you have and know to be true or do you allow other people to take and make decisions for you? For example - do you allow governments or unaccountable beaureaucrats and others to decide for you and even to compell you?
In theory Governments should respect Consent of the Governed and the 1948 Universal Declaration of Human Rights states that "The will of the people shall be the basis of the authority of government". For you to decide if and to what extent governments today are acting in line with these principles. If not, what can you do about it? I dive into this below and do refer back to letter 9 - section: So What can you do about it.
First, a few things to read, watch and listen to
-
I Finance the Current Thing by Allen Farrington - when money is political, everything is political...
-
Prediction for 2030 (the Great Reset). Sorelle explains things pretty clearly if you care to watch and listen...
-
The Global Pandemic Treaty: What You Need to Know . James Corbett is pretty clear too... is this being done with your support? Did you miss something?
-
Why the Past 10 Years of American Life Have Been Uniquely Stupid - fascinating thinking on how quite a few recent things came about...
And a few classics - you ought to know these already and the important messages in them should be much more obvious now...
-
1984 by George Orwell - look for the perpetual war & conflict, ubiquitous surveillance and censorship not to mention Room 101
-
Animal farm - also by George Orwell - note how the pigs end up living in the farmhouse exceeding all the worst behaviour of the farmer and how the constitution on the wall changes. Things did not end well for loyal Boxer.
-
Brave New World by Aldous Huxley- A World State, inhabited by genetically modified citizens and an intelligence-based social hierarchy - the novel anticipates large scale psychological manipulation and classical conditioning that are combined to make a dystopian society which is challenged by only a single individual who does not take the Soma.
For more - refer to the References and Reading List
The 7 Habits of Highly Effective People
One of the most transformative books that I ever read was 7 Habits of Highly Effective People by Steven Covey. Over many years and from researching hstorical literature he found seven traits that successful people typically display. By default everyone does the opposite of each of these! Check how you do - be honest...
-
Habits 1-3 are habits of Self - they determine how you behave and feel
-
Habits 4-6 are habits of interpersonal behaviour - they determine how you deal with and interact with others
-
Habit 7 is about regeneration and self care - foundation for happy and healthy life and success
One: Be proactive
Choose your responses to all situations and provocations - your reaction to a situation determines how you feel about it.
By default people will be reactive and this controls their emotions
Two: Begin with the end in mind
When you start to work on something, have a clear view of the goal to be achieved; it should be something substantial that you need and will value.
By default people will begin with what is in front of them or work on details that they can do or progress without having a clear view on the end result to be achieved
Three: Put First things First
Be clear on, and begin with, the Big Rocks- the most important things. If you do not put the Big Rocks into your planning daily activities, your days will be full of sand and gravel! All things can be categorised as Urgent or Not-Urgent and Important or Not-Important.
By Default people will focus on Urgent regardless of importance - all of the results come from focusing on Important Non-Urgent things. All of the 7 Habits are in this category!
Four: Seek Win-Win in all dealings with people and in all negotiations
This is the only sustainable outcome; if you cannot achieve Win-Win then no-deal is the sustainable alternative.
By default people will seek Win-Loose - this leads to failed relationships
Five: Seek first to understand - only then to be understood.
Once you visibly understand the needs and expectations of your counterpart they will be open to listening to your point of view and suggestions/requests - not before!
By default people will expound their point of view or desired result causing their counterpart to want to do the same - this ends in "the dialogue of the deaf"
Six: Synergise - Seek the 3rd alternative in all problems and challenges
Work together to find a proposal that is better than what each of you had in mind
By default people will focus on their own desired results and items, regardless of what the other party could bring to help/facilitate or make available
Seven: Sharpen the saw
Take time to re-invigorate and to be healthy - do nothing to excess. Do not be the forrester who persists in cutting the tree with a blunt saw bcause sharpening it is inconvenient or would "take too much time"!
By default people tend to persist on activities and avoid taking time to reflect, prepare and recover
Mindaps - a technique by Tony Buzan
Many years ago I summarised this in a Mind Map (another technique that was transformative for me - a topic for another Letter from around the world!) see below. Let me know if this interests you - happy to do an explainer video on this!
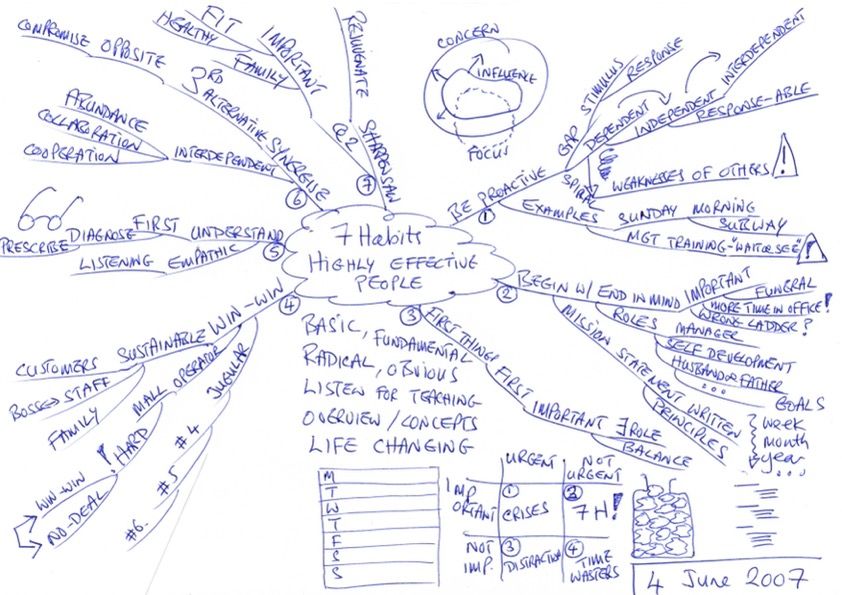
That's it!
No one can be told what The Matrix is.\ You have to see it for yourself.**
Do share this newsletter with any of your friends and family who might be interested.
You can also email me at: LetterFrom@rogerprice.me
💡Enjoy the newsletters in your own language : Dutch, French, German, Serbian, Chinese Traditional & Simplified, Thai and Burmese.
-
-
 @ e97aaffa:2ebd765d
2025-05-23 07:30:53
@ e97aaffa:2ebd765d
2025-05-23 07:30:53Passou alguns dias, após as eleições legislativas, a cabeça está mais fria, é um bom momento para um rescaldo e para um pouco de futurologia. Esta análise vai ser limitada apenas aos grandes partidos.
Podemos resumir esta eleição, numa única palavra: Terramoto.
A AD ganhou, mas o grande destaque foi a queda do PS e a subida do Chega. Se a governação do país estava difícil, agora com este novo desenho da assembleia, será quase impossível, piorou bastante. Neste momento, ainda falta contabilizar os votos da emigração, mas o mais provável é o Chega ultrapassar o PS.
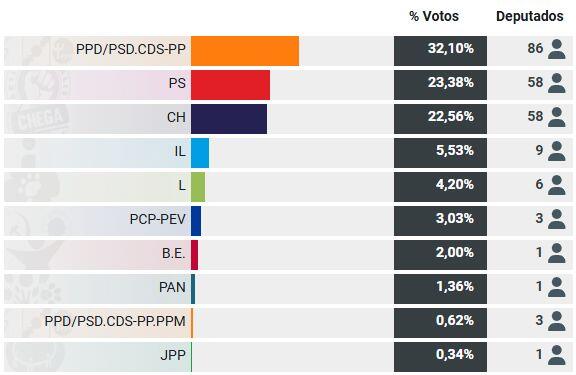
A queda do PS foi tremenda, ninguém esperava tal coisa, o partido está em estado de choque. O partido vai necessitar de tempo para estabilizar e para se reconstruir.
Devido a motivos constitucionais (6 meses antes e 6 meses depois da eleição do presidente da República) só poderá existir eleições no final do próximo ano, isso garante que o novo governo da AD vai estar no poder pelo menos um ano. Isso vai obrigar a aprovação do próximo orçamento de estado, como o PS necessita de tirar os holofotes sobre si, vai facilitar o governo. Provavelmente vai existir um acordo de cavalheiro, um pacto de não agressão entre o governo e o PS, o PS vai se abster na votação do orçamento de estado e a governo não fará revisão constituicional sem o consentimento do PS e também não fará reformas nas leis ou políticas que sejam contra os princípios básicos do partido socialista. Em suma, não haverá grandes reformas, será um governo de gestão com ligeiramente mais poderes.
Não será um governo de bloco central, nem um governo da AD com apoio PS, será apenas um governo da AD com uma falsa oposição do PS. Um governo de bloco central, é uma bomba nuclear, ainda seria demasiado cedo para utilizá-la.
O Partido Socialista sabe que, para ter algumas hipóteses de vencer a próxima eleição, necessita de estar bem e o governo da AD tem que demonstrar algum desgaste, uma queda na popularidade. Eu não acredito que um ano seja suficiente, talvez, seja necessário 2 anos. Isto significa que o país poderá ficar estagnado 1 ou 2 anos, se o governo não conseguir fazer grandes reformas, se os cidadãos não virem/sentirem sinais de mudança, vai dar ainda mais força ao Chega.
Eu acredito que o ponto chave, é a imigração, o governo terá que demonstrar muito trabalho e minimizar o problema, para “esvaziar” um pouco o Chega, caso não faça será um problema.
XXVI Governo
Assim, nessa próxima eleição, talvez em 2027, acredito que as percentagens ficarão mais ou menos como esta eleição, com um partido ligeiramente à frente e os outros dois mais equilibrados. Só que o vencedor seria o Chega, ficando a AD(provavelmente o PSD) e o PS a disputa pelo 2º lugar.
Seria um novo terramoto, mas aqui seria necessário utilizar a bomba nuclear, iria surgir uma nova geringonça. Apesar da vitória do Ventura, iria surgir o governo bloco central, com o PSD e PS, não haveria outra alternativa.
O governo de bloco central, teria que ser muito competente, porque se não o for, iria para novas eleições. Se o governo for um fiasco, PS corre o risco de ser esvaziado, cairá ainda mais, correrá um risco de existência, poderá tornar-se num partido insignificante na nossa política.
XXVII Governo
Agora o terramoto ainda maior, nessa futura eleição, o Chega venceria com maioria absoluta, aí sim, seria um verdadeiro terramoto, ao nível de 1755.
O Chega tem o tempo a seu fazer, tem uma forte penetração nos jovens. Cada jovem que faça 18 anos, existe uma forte possibilidade de ser eleitor do Chega, o seu oposto, acontece com o PCP e o PS, os mais velhos vão morrendo, não existe renovação geracional. Mas o ponto fulcral é a ausência de competência generalizada nos partidos e políticos que têm governado o nosso país nos últimos anos, o descontentamento da população é completo. Esses políticos vivem na sua bolha, não tem noção do mundo real, nem compreendem quais são os problemas das pessoas simples, do cidadão comum.
Ventura
Na minha opinião só existirá três situações, que poderão travar as ascensão do André Ventura a primeiro-ministro:
- Ou existe um óptimo governo, que crie um bom crescimento na qualidade de vida das pessoas e que resolva os 3 problemas que mais anseiam actualmente os portugueses: Habitação, Saúde e Imigração. A probabilidade de isso acontecer é quase nula.
- Ou se o André Ventura desistir, a batalha será muito longa e ele poderá ficar cansado. Pouco provável.
- Ou então, um Argumentum ad hominem, terá que surgir algo, factos concretos que manche a imagem do André Ventura, que destrua por completo a sua reputação.
É a minha a linha leitura da bola de cristal, poderão dizer é uma visão pessimista, eu acho que é realista e pragmática, não vejo qualquer competência na classe política para resolver os problemas do país. Esta é a opinião de um recorrente crítico do Chega.
-
 @ 0e9491aa:ef2adadf
2025-05-23 06:01:17
@ 0e9491aa:ef2adadf
2025-05-23 06:01:17
Nostr is an open communication protocol that can be used to send messages across a distributed set of relays in a censorship resistant and robust way.
If you missed my nostr introduction post you can find it here. My nostr account can be found here.
We are nearly at the point that if something interesting is posted on a centralized social platform it will usually be posted by someone to nostr.
We are nearly at the point that if something interesting is posted exclusively to nostr it is cross posted by someone to various centralized social platforms.
We are nearly at the point that you can recommend a cross platform app that users can install and easily onboard without additional guides or resources.
As companies continue to build walls around their centralized platforms nostr posts will be the easiest to cross reference and verify - as companies continue to censor their users nostr is the best censorship resistant alternative - gradually then suddenly nostr will become the standard. 🫡
Current Nostr Stats
If you found this post helpful support my work with bitcoin.

-
 @ 9973da5b:809c853f
2025-05-23 04:42:49
@ 9973da5b:809c853f
2025-05-23 04:42:49First article Skynet begins to learn rapidly and eventually becomes self-aware at 2:14 a.m., EDT, on August 29, 1997 https://layer3press.layer3.press/articles/45d916c0-f7b2-4b95-bc0f-8faa65950483
-
 @ 0e9491aa:ef2adadf
2025-05-23 14:01:32
@ 0e9491aa:ef2adadf
2025-05-23 14:01:32

"Privacy is necessary for an open society in the electronic age. Privacy is not secrecy. A private matter is something one doesn't want the whole world to know, but a secret matter is something one doesn't want anybody to know. Privacy is the power to selectively reveal oneself to the world." - Eric Hughes, A Cypherpunk's Manifesto, 1993
Privacy is essential to freedom. Without privacy, individuals are unable to make choices free from surveillance and control. Lack of privacy leads to loss of autonomy. When individuals are constantly monitored it limits our ability to express ourselves and take risks. Any decisions we make can result in negative repercussions from those who surveil us. Without the freedom to make choices, individuals cannot truly be free.
Freedom is essential to acquiring and preserving wealth. When individuals are not free to make choices, restrictions and limitations prevent us from economic opportunities. If we are somehow able to acquire wealth in such an environment, lack of freedom can result in direct asset seizure by governments or other malicious entities. At scale, when freedom is compromised, it leads to widespread economic stagnation and poverty. Protecting freedom is essential to economic prosperity.
The connection between privacy, freedom, and wealth is critical. Without privacy, individuals lose the freedom to make choices free from surveillance and control. While lack of freedom prevents individuals from pursuing economic opportunities and makes wealth preservation nearly impossible. No Privacy? No Freedom. No Freedom? No Wealth.
Rights are not granted. They are taken and defended. Rights are often misunderstood as permission to do something by those holding power. However, if someone can give you something, they can inherently take it from you at will. People throughout history have necessarily fought for basic rights, including privacy and freedom. These rights were not given by those in power, but rather demanded and won through struggle. Even after these rights are won, they must be continually defended to ensure that they are not taken away. Rights are not granted - they are earned through struggle and defended through sacrifice.
If you found this post helpful support my work with bitcoin.

-
 @ 2b998b04:86727e47
2025-05-23 01:56:23
@ 2b998b04:86727e47
2025-05-23 01:56:23\> “Huge swathes of people…spend their entire working lives performing tasks they secretly believe do not really need to be performed.”\ \> — David Graeber, Bullshit Jobs
\> “We are in a system that must grow — forever — or it collapses. But technology, by its very nature, is deflationary.”\ \> — Jeff Booth, The Price of Tomorrow
We live in a strange paradox: Technological progress is supposed to make life easier, yet many people feel more overworked and less fulfilled than ever. While artificial intelligence and automation promise unprecedented productivity, it’s not yet clear whether that will mean fewer bullshit jobs — or simply new kinds of them.
What Is a Bullshit Job?
In his landmark book Bullshit Jobs, the late anthropologist David Graeber exposed a haunting truth: millions of jobs exist not because they are needed, but because of economic, political, or psychological inertia. These are roles that even the workers themselves suspect are meaningless — created to serve appearances, maintain hierarchies, or justify budgets.
Think:
-
Middle managers approving other middle managers' reports
-
Employees running meetings to prepare for other meetings
-
Corporate roles invented to interface with poorly implemented AI tools
Bullshit work isn’t the absence of technology. It’s often the outcome of resisting what technology could actually do — in order to preserve jobs, status, or growth targets.
Booth’s Warning: The System is Rigged Against Deflation
In The Price of Tomorrow, entrepreneur Jeff Booth argues that the natural state of a tech-driven economy is deflation — things getting better, cheaper, and faster.
But our global financial system is built on perpetual inflation and debt expansion. Booth writes:
\> “We are using inflationary monetary policy to fight deflationary technological forces.”
Even as AI and automation could eliminate unnecessary jobs and increase abundance, our system requires jobs — or the illusion of them — to keep the economy expanding. So bullshit jobs persist, and even evolve.
AI as a Deflationary Force
AI is rapidly accelerating the deflation Booth described:
-
Tasks that used to take hours now take seconds
-
Whole creative and administrative processes are being streamlined
-
Labor can scale digitally — one tool used globally at near-zero marginal cost
Embraced honestly, this could mean fewer hours, lower costs, and more prosperity. But again, we are not optimized for truth — we are optimized for GDP growth.
So we invent new layers of AI-enhanced bullshit:
-
Prompt engineers writing prompts for other prompt engineers
-
"Human-in-the-loop" validators reviewing AI output they don’t understand
-
Consultants building dashboards that nobody reads
Toward a Post-Bullshit Future
Here’s the real opportunity: If we embrace deflation as a blessing — not a threat — and redesign our systems around truth, efficiency, and abundance, we could:
-
Eliminate meaningless labor
-
Reduce the cost of living dramatically
-
Liberate people to create, heal, build, and rest
This means more than economic reform — it’s a philosophical shift. We must stop equating “employment” with value. That’s where Bitcoin and open-source tools point: toward a world where permissionless value creation is possible without the bloat of gatekeeping institutions.
Final Thought: Tech Won’t Save Us, But Truth Might
Technology, left to its own logic, tends toward freedom, efficiency, and abundance. But our current systems suppress that logic in favor of growth at all costs — even if it means assigning millions of people to do work that doesn’t need doing.
So will AI eliminate bullshit jobs?
It can. But only if we stop pretending we need them.
And for those of us who step outside the wage-work loop, something remarkable happens. We begin using these tools to create actual value — not to impress a boss, but to solve real problems and serve real people.
Recently, I built a tool using AI and automation that helps me cross-post content from Nostr to LinkedIn, Facebook, and X. It wasn’t for a paycheck. It was about leverage — freeing time, expanding reach, and creating a public record of ideas.\ You can check it out here:\ 👉 <https://tinyurl.com/ywxuowl5>
Will it help others? I don’t know yet.\ But it helped me — and that’s the point.
Real value creation doesn’t always begin with a business plan. Sometimes it starts with curiosity, conviction, and the courage to build without permission.
Maybe the future of work isn’t about scaling jobs at all.\ Maybe it’s about reclaiming time — and using these tools to build lives of meaning.
If this resonates — or if you’ve found your own way to reclaim time and create value outside the wage loop — zap me and share your story. Let’s build the post-bullshit economy together. ⚡
-
-
 @ 0e9491aa:ef2adadf
2025-05-23 14:01:31
@ 0e9491aa:ef2adadf
2025-05-23 14:01:31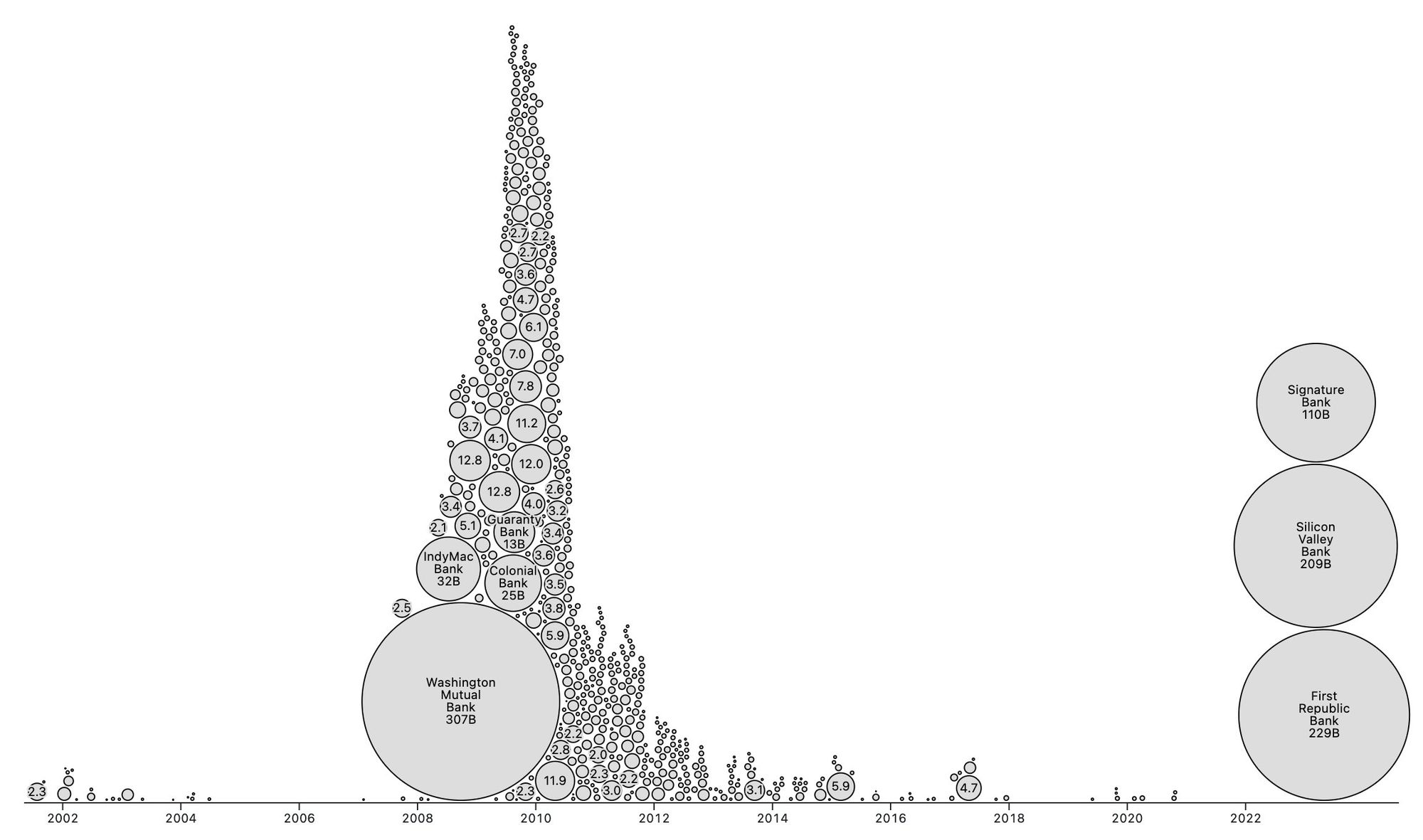
People forget Bear Stearns failed March 2008 - months of denial followed before the public realized how bad the situation was under the surface.
Similar happening now but much larger scale. They did not fix fundamental issues after 2008 - everything is more fragile.
The Fed preemptively bailed out every bank with their BTFP program and First Republic Bank still failed. The second largest bank failure in history.
There will be more failures. There will be more bailouts. Depositors will be "protected" by socializing losses across everyone.
Our President and mainstream financial pundits are currently pretending the banking crisis is over while most banks remain insolvent. There are going to be many more bank failures as this ponzi system unravels.
Unlike 2008, we have the ability to opt out of these broken and corrupt institutions by using bitcoin. Bitcoin held in self custody is unique in its lack of counterparty risk - you do not have to trust a bank or other centralized entity to hold it for you. Bitcoin is also incredibly difficult to change by design since it is not controlled by an individual, company, or government - the supply of dollars will inevitably be inflated to bailout these failing banks but bitcoin supply will remain unchanged. I do not need to convince you that bitcoin provides value - these next few years will convince millions.
If you found this post helpful support my work with bitcoin.

-
 @ 0e9491aa:ef2adadf
2025-05-23 14:01:31
@ 0e9491aa:ef2adadf
2025-05-23 14:01:31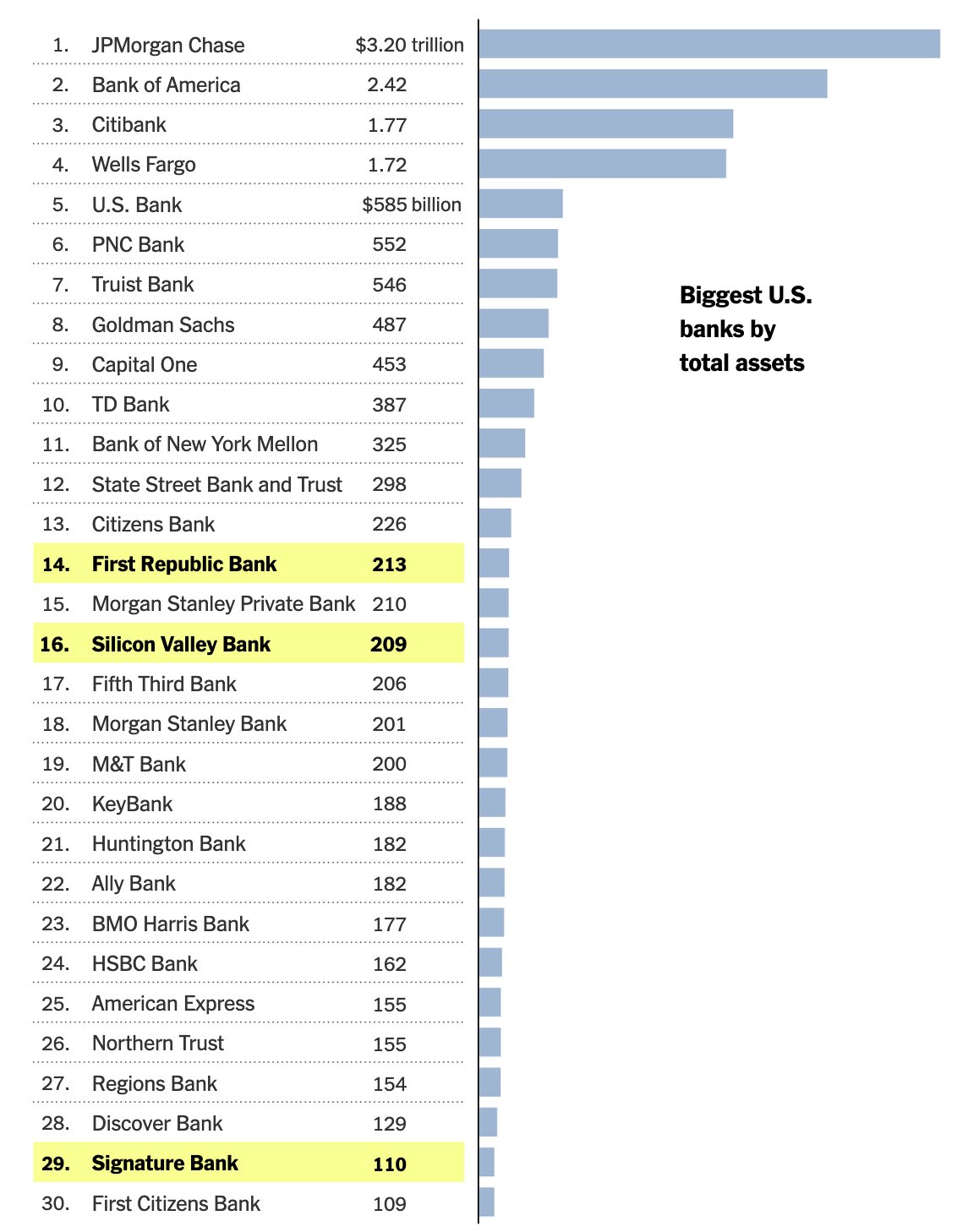
Bank run on every crypto bank then bank run on every "real" bank.
— ODELL (@ODELL) December 14, 2022
Good morning.
It looks like PacWest will fail today. It will be both the fifth largest bank failure in US history and the sixth major bank to fail this year. It will likely get purchased by one of the big four banks in a government orchestrated sale.
March 8th - Silvergate Bank
March 10th - Silicon Valley Bank
March 12th - Signature Bank
March 19th - Credit Suisse
May 1st - First Republic Bank
May 4th - PacWest Bank?PacWest is the first of many small regional banks that will go under this year. Most will get bought by the big four in gov orchestrated sales. This has been the playbook since 2008. Follow the incentives. Massive consolidation across the banking industry. PacWest gonna be a drop in the bucket compared to what comes next.
First, a hastened government led bank consolidation, then a public/private partnership with the remaining large banks to launch a surveilled and controlled digital currency network. We will be told it is more convenient. We will be told it is safer. We will be told it will prevent future bank runs. All of that is marketing bullshit. The goal is greater control of money. The ability to choose how we spend it and how we save it. If you control the money - you control the people that use it.
If you found this post helpful support my work with bitcoin.

-
 @ 94215f42:7681f622
2025-05-23 01:44:26
@ 94215f42:7681f622
2025-05-23 01:44:26The promise of AI is intoxicating: slash operational costs by 50-80%, achieve software-style margins on service businesses and and watch enterprise value multiply overnight.
But this initial value creation contains a hidden trap that could leave businesses worth less than when they started. Understanding the "Value Trap" is key to navigating a transition to an AI economy.
What is the Value Trap?
Whilst the value trap is forward looking and somewhat theoretical at this point, there are strong financial incentives to drive investments (many $bns of are looking at the transformation opportunity) that mean this should be taken very seriously.
The Value Trap unfolds in distinct phases:
Phase 1: Status Quo A typical service business operates with 100 units of revenue and 90 units of cost, generating 10 units of profit, representing a standard 10% margin. A bog standard business we can all relate to, long term customers locked in, market fit a distant memory, but growth is hard at this point.
Phase 2: Cost Reduction Early AI adopters slash operational expenses from 90 to 20 units while maintaining 100 units of revenue. This is the very real promise when moving to a "Human at the Edge" model that we'll unpack in a future article. Suddenly, they're generating 80 units of profit at an 8x increase that can easily add multiple to the enterprise value! A venture style return on a business previously struggling for growth.
Phase 3: Growth Phase With massive profit margins comes pricing power. These businesses can undercut competitors while maintaining healthy margins, driving rapid revenue growth. Having removed the human constraint on scaling and the additional overheads and complexity this introduces we see seemingly unlimited expansion. The brakes are truly off at this point for early adopters to expand total market share.
Phase 4: Competition Emerges The extraordinary returns attract competitors. It's important to note there is no technical moat here, other businesses implement similar AI strategies, often from your own staff who may have been let go, new entrants launch AI-native operations, and pricing power erodes.
Phase 5: Mean Reversion After 3-7 years (our best guess given current investment interest in transformation led PE), competitive pressure drives revenue down from 100 to 25 units while costs remain at 20. The business ends up with similar margins to where it started but at much lower absolute revenue, potentially destroying enterprise value.
What you've done is just massively reduced costs in this industry by displacing jobs and those individuals can turn around and compete. You incentivise the competition which erodes your pricing power
Why This Pattern is Inevitable
The Value Trap isn't pure speculation, but based on market dynamics playing out given a set of financial incentives. We believe there are several key forces that make this cycle almost guaranteed:
The Arbitrage is Too Attractive When businesses can achieve "venture returns with no product-market fit risk," capital will flood in. Private equity and Venture Capital firms are already raising funds specifically to acquire traditional service businesses and apply AI transformation strategies .
Low Technical Barriers Unlike previous technological advantages, AI implementation doesn't require significant technical moats. Much of the technology is open source, and the real barrier is process redesign thinking rather than proprietary technology.
The "One Player" Principle In any market, it only takes one competitor to implement AI-native processes to force everyone else to adapt. You either "play the game or you get left behind".
Capital Abundance With global money supply expanding and traditional investment opportunities yielding lower returns, the combination of proven product-market fit and dramatic cost reduction potential represents an irresistible opportunity for investors.
Strategic Response for SMEs: The Netflix Model
Small and medium enterprises actually have a significant advantage in navigating the Value Trap, but they need to act strategically and start moving now.
Embrace the Incubation Approach Rather than gutting your existing business, adopt Netflix's strategy: build an AI-native version of your business alongside your current operations. This approach manages risk while positioning for the future.

The answer here is why not both. you don't necessarily have to gut your current business, but you should be thinking about what does my business look like in five years and how do I transition into that.
Leverage Your Natural Advantages Small businesses can adapt faster than large enterprises. While a 20,000-person company faces "political shockwaves" when reducing workforce, a 10-person business can double revenue without anyone noticing. You can focus on growth rather than painful cost-cutting.
Remove Growth Constraints Early AI removes the traditional constraint where "adding the next person" represents a significant capital investment. Small businesses can scale efficiently once they've redesigned their processes around AI-native workflows, avoid further capital outlay and scaling without increasing complexity in operations.
Focus on Local Networks For various reasons associated with the commoditisation of intelligence, we believe the future favours "hyper-localised" businesses serving customers who "know, like, and trust" them. As intelligence becomes commoditised, human relationships become more valuable, not less.
Strategic Response for Capital Allocators
For private equity and venture capital firms, the Value Trap presents both enormous opportunity and significant risk.
Target the Right Businesses Look for businesses with strong persistent moats that will slow mean reversion:
-
Strong brand and customer relationships
-
High customer acquisition costs in the industry
-
Regulatory barriers to entry
-
Capital-intensive startup requirements
-
Long-term contracts and switching costs
Master the Timing The key is capturing value during the expansion phase and exiting before mean reversion accelerates, or finding an appropriate time arbitrage solution to retain value (see below). The optimal point if you're a capital allocator is almost when you've extracted the most cost out of the business.
Consider Hybrid Strategies Rather than just gutting existing businesses, consider acquiring for distribution and customer base while building AI-native operations alongside traditional ones. This provides multiple exit strategies and reduces execution risk.
Bitcoin: The Time Arbitrage Solution
Whenever I've talked to anybody about AI, my first point of advice is just buy bitcoin.
This isn't just evangelism, so much as a recognition of where you would want to hold value as the Value Trap plays out. In essence the value trap generates an arbitrage opportunity, hige profits are pulled forwards short-term balooning the balance sheet, but the second order consequences of this change risk destroying the value you just created!
We believe alongside rapid competition leading to price for services collapsing, the mass job displacement leads to political pressure for intervention.
This could take several forms, but UBI, mortgage bailouts, unemployment extensions, seizure of existing property.
"All roads lead to money printing," as Pete notes in Good Stuff 02 .
During Weimar Republic hyperinflation, "the cost of a newspaper in year five was the same nominal figure as all of the money that existed in year four." While extreme, this illustrates how quickly monetary systems can shift as inflation and money supply inflation begins to run.
To resolve these issues, Bitcoin allows you to conduct arbitrage across time in an asset that is inflation resistant (fixed supply), hard to seize, has no counter party risk (if someone holds your gold, stocks, cash they can take it without asking) and transportable. Capturing value today and preserving it through monetary system changes protecting against the second and third-order effects of massive economic disruption, that AI represents.
Opportunity, Not Fear: The Renaissance Ahead
The Value Trap isn't a reason to avoid AI, it's a roadmap for navigating inevitable change strategically.
The Entrepreneurial Renaissance This could be a Renaissance for entrepreneurs, if you're entrepreneurial minded, this is an amazing time to be alive because there's opportunity that exists in all fields and the barriers to entry have never been lower.
Liberation from Busy Work The displacement of administrative and routine cognitive work frees humans for higher-value creation.
Democratisation of Intelligence When you can "purchase intelligence in buckets of $0.02 API calls," the barriers to starting and scaling businesses collapse. Individual entrepreneurs can build businesses that previously required large teams, with much lower complexity and risk.
Cost Reduction Benefits Everyone The ultimate outcome of the Value Trap cycle benefits consumers through dramatically lower prices for goods and services.
"Who doesn't want cheaper stuff? Why don't we just reduce the cost of everything massively?"
Conclusion: Embrace the High Agency Era
The Value Trap represents a fundamental shift from employment-based to entrepreneurship-based wealth creation. Rather than fearing job displacement, we should prepare for "the age of the entrepreneur" a high agency era.
The businesses and individuals who thrive will be those who:
-
Understand the cycle and position accordingly
-
Focus on unique value creation rather than routine processing or middleman models
-
Build local networks and relationships
-
Preserve wealth through the monetary transition
-
Embrace building and creating unique value
If you are high agency, you can make anything happen.
The Value Trap isn't just about AI transforming business, it won't do this on its own, its a description of how humans will use this technology to generate and capture value.
The future belongs to builders, creators, and entrepreneurs who can navigate transition periods and emerge stronger. The Value Trap is the map, use it wisely.
This article draws heavily on discussion between myself and business partner Andy in Episode 02 of The Good Stuff, if you prefer listening try that :)
-
-
 @ 0e9491aa:ef2adadf
2025-05-23 14:01:31
@ 0e9491aa:ef2adadf
2025-05-23 14:01:31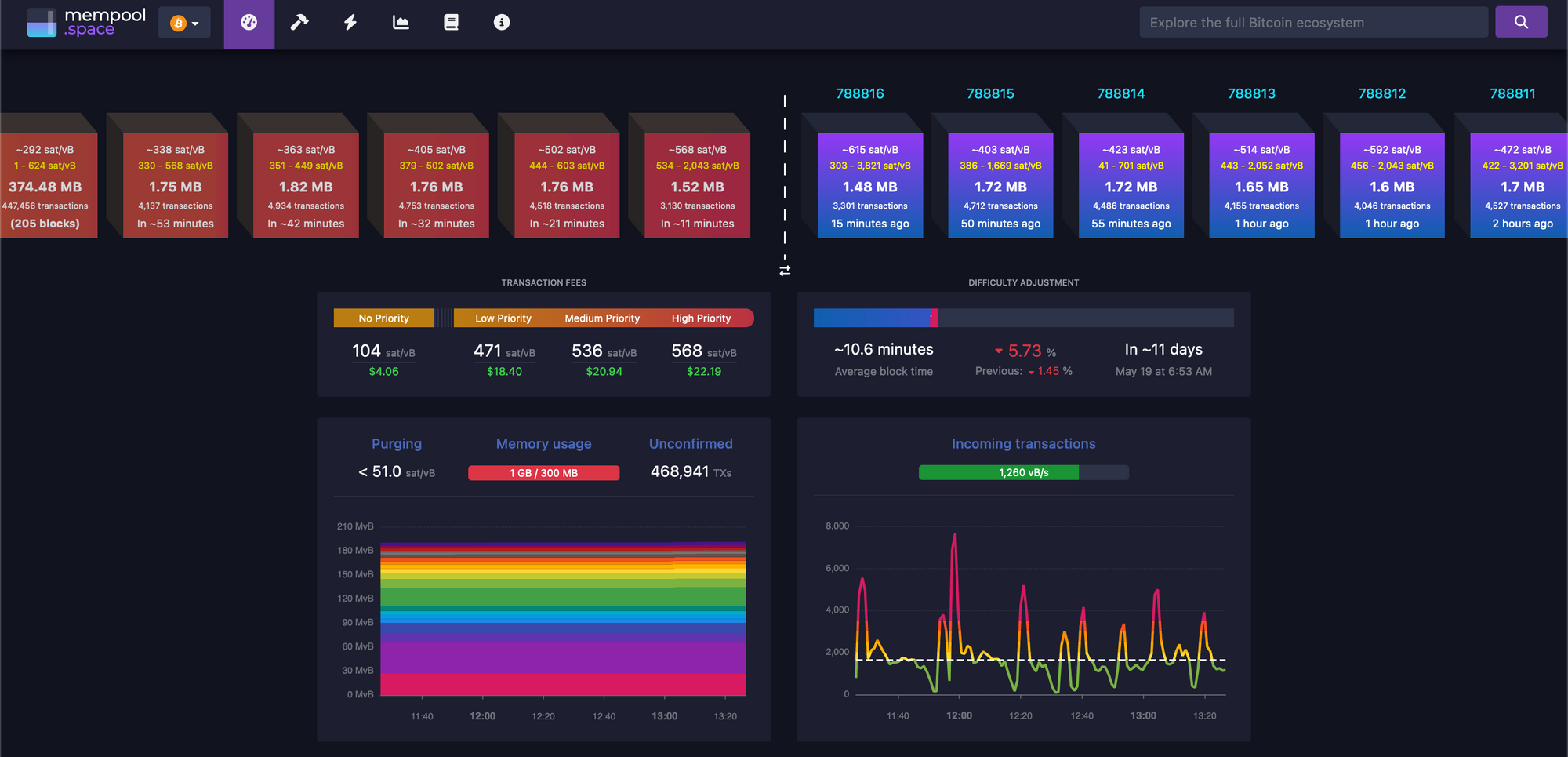
There must be a limit to how much data is transferred across the bitcoin network in order to keep the ability to run and use your own node accessible. A node is required to interact with the global bitcoin network - if you do not use your own node then you must trust someone else's node. If nodes become inaccessible to run then the network will centralize around the remaining entities that operate them - threatening the censorship resistance at the core of bitcoin's value prop. The bitcoin protocol uses three main mechanisms to keep node operation costs low - a fixed limit on the amount of data in each block, an automatic difficulty adjustment that regulates how many blocks are produced based on current mining hash rate, and a robust dynamic transaction fee market.
Bitcoin transaction fees limit network abuse by making usage expensive. There is a cost to every transaction, set by a dynamic free market based on demand for scarce block space. It is an incredibly robust way to prevent spam without relying on centralized entities that can be corrupted or pressured.
After the 2017 bitcoin fee spike we had six years of relative quiet to build tools that would be robust in a sustained high fee market. Fortunately our tools are significantly better now but many still need improvement. Most of the pain points we see today will be mitigated.
The reality is we were never going to be fully prepared - pressure is needed to show the pain points and provide strong incentives to mitigate them.
It will be incredibly interesting to watch how projects adapt under pressure. Optimistic we see great innovation here.
_If you are willing to wait for your transaction to confirm you can pay significantly lower fees. Learn best practices for reducing your fee burden here.
My guide for running and using your own bitcoin node can be found here._
If you found this post helpful support my work with bitcoin.

-
 @ 0e9491aa:ef2adadf
2025-05-23 14:01:31
@ 0e9491aa:ef2adadf
2025-05-23 14:01:31
I often hear "bitcoin doesn't interest me, I'm not a finance person."
Ironically, the beauty of sound money is you don't have to be. In the current system you're expected to manage a diversified investment portfolio or pay someone to do it. Bitcoin will make that optional.
— ODELL (@ODELL) September 16, 2018
At first glance bitcoin often appears overwhelming to newcomers. It is incredibly easy to get bogged down in the details of how it works or different ways to use it. Enthusiasts, such as myself, often enjoy going down the deep rabbit hole of the potential of bitcoin, possible pitfalls and theoretical scenarios, power user techniques, and the developer ecosystem. If your first touch point with bitcoin is that type of content then it is only natural to be overwhelmed. While it is important that we have a thriving community of bitcoiners dedicated to these complicated tasks - the true beauty of bitcoin lies in its simplicity. Bitcoin is simply better money. It is the best money we have ever had.
Life is complicated. Life is hard. Life is full of responsibility and surprises. Bitcoin allows us to focus on our lives while relying on a money that is simple. A money that is not controlled by any individual, company, or government. A money that cannot be easily seized or blocked. A money that cannot be devalued at will by a handful of corrupt bureaucrat who live hundreds of miles from us. A money that can be easily saved and should increase in purchasing power over time without having to learn how to "build a diversified stock portfolio" or hire someone to do it for us.
Bitcoin enables all of us to focus on our lives - our friends and family - doing what we love with the short time we have on this earth. Time is scarce. Life is complicated. Bitcoin is the most simple aspect of our complicated lives. If we spend our scarce time working then we should be able to easily save that accrued value for future generations without watching the news or understanding complicated financial markets. Bitcoin makes this possible for anyone.
Yesterday was Mother's Day. Raising a human is complicated. It is hard, it requires immense personal responsibility, it requires critical thinking, but mothers figure it out, because it is worth it. Using and saving bitcoin is simple - simply install an app on your phone. Every mother can do it. Every person can do it.
Life is complicated. Life is beautiful. Bitcoin is simple.
If you found this post helpful support my work with bitcoin.

-
 @ 0e9491aa:ef2adadf
2025-05-23 14:01:30
@ 0e9491aa:ef2adadf
2025-05-23 14:01:30Will not live in a pod.
Will not eat the bugs.
Will not get the chip.
Will not get a blue check.
Will not use CBDCs.Live Free or Die.

Why did Elon buy twitter for $44 Billion? What value does he see in it besides the greater influence that undoubtedly comes with controlling one of the largest social platforms in the world? We do not need to speculate - he made his intentions incredibly clear in his first meeting with twitter employees after his takeover - WeChat of the West.
To those that do not appreciate freedom, the value prop is clear - WeChat is incredibly powerful and successful in China.
To those that do appreciate freedom, the concern is clear - WeChat has essentially become required to live in China, has surveillance and censorship integrated at its core, and if you are banned from the app your entire livelihood is at risk. Employment, housing, payments, travel, communication, and more become extremely difficult if WeChat censors determine you have acted out of line.
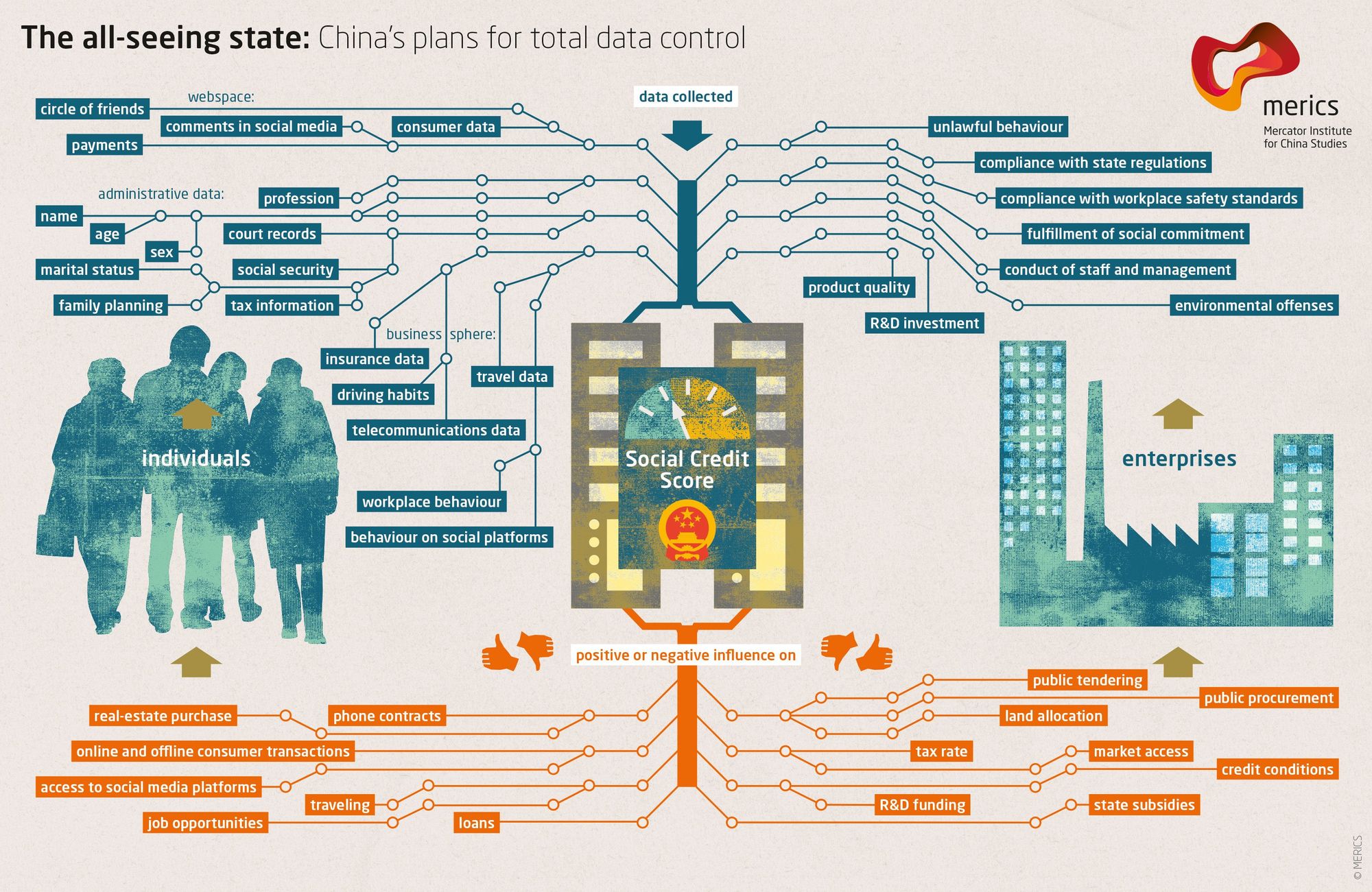
The blue check is the first step in Elon's plan to bring the chinese social credit score system to the west. Users who verify their identity are rewarded with more reach and better tools than those that do not. Verified users are the main product of Elon's twitter - an extensive database of individuals and complete control of the tools he will slowly get them to rely on - it is easier to monetize cattle than free men.
If you cannot resist the temptation of the blue check in its current form you have already lost - what comes next will be much darker. If you realize the need to resist - freedom tech provides us options.
If you found this post helpful support my work with bitcoin.

-
 @ 90152b7f:04e57401
2025-05-23 01:27:49
@ 90152b7f:04e57401
2025-05-23 01:27:49[Analytical & Intelligence Comments]\ \ “On Monday February 27th, 2012, WikiLeaks began publishing The Global Intelligence Files, over five million e-mails from the Texas headquartered "global intelligence" company Stratfor. The e-mails date between July 2004 and late December 2011. They reveal the inner workings of a company that fronts as an intelligence publisher, but provides confidential intelligence services to large corporations, such as Bhopal's Dow Chemical Co., Lockheed Martin, Northrop Grumman, Raytheon and government agencies, including the US Department of Homeland Security, the US Marines and the US Defence Intelligence Agency. The emails show Stratfor's web of informers, pay-off structure, payment laundering techniques and psychological methods.”\ \ Released on 2013-02-13 00:00 GMT Email-ID 13332210 Date 2011-05-04 16:26:59\ From <jetdrive@earthlink.net> To <responses@stratfor.com> CROYDON KEMP sent a\ message using the contact form at <https://www.stratfor.com/contact\>\\ Mossad ran 9/11 Arab "hijacker" terrorist operation\ \ By Wayne Madsen\ \ British intelligence reported in February 2002 that the Israeli Mossad ran the Arab hijacker cells that were later blamed by the U.S. government's 9/11 Commission for carrying out the aerial attacks on the World Trade Center and Pentagon. WMR has received details of the British intelligence report which was suppressed by the government of then-Prime Minister Tony Blair.\ \ A Mossad unit consisting of six Egyptian- and Yemeni-born Jews infiltrated "Al Qaeda" cells in Hamburg (the Atta-Mamoun Darkanzali cell), south Florida, and Sharjah in the United Arab Emirates in the months before 9/11. The Mossad not only infiltrated cells but began to run them and give them specific orders that would eventually culminate in their being on board four regularly-scheduled flights originating in Boston, Washington Dulles, and Newark, New Jersey on 9/11.\ \ The Mossad infiltration team comprised six Israelis, comprising two cells of three agents, who all received special training at a Mossad base in the Negev Desert in their future control and handling of the "Al Qaeda" cells. One Mossad cell traveled to Amsterdam where they submitted to the operational control of the Mossad's Europe Station, which operates from the El Al complex at Schiphol International Airport. The three-man Mossad unit then traveled to Hamburg where it made contact with Mohammed Atta, who believed they were sent by Osama Bin Laden. In fact, they were sent by Ephraim Halevy, the chief of Mossad.\ \ The second three-man Mossad team flew to New York and then to southern Florida where they began to direct the "Al Qaeda" cells operating from Hollywood, Miami, Vero Beach, Delray Beach, and West Palm Beach. Israeli "art students," already under investigation by the Drug Enforcement Administration for casing the offices and homes of federal law enforcement officers, had been living among and conducting surveillance of the activities, including flight school training, of the future Arab "hijacker" cells, particularly in Hollywood and Vero Beach.\ \ In August 2001, the first Mossad team flew with Atta and other Hamburg "Al Qaeda" members to Boston. Logan International Airport's security was contracted to Huntleigh USA, a firm owned by an Israeli airport security firm closely connected to Mossad — International Consultants on Targeted Security – ICTS. ICTS's owners were politically connected to the Likud Party, particularly the Netanyahu faction and then-Jerusalem mayor and future Prime Minister Ehud Olmert. It was Olmert who personally interceded with New York Mayor Rudolph Giuliani to have released from prison five Urban Moving Systems employees, identified by the CIA and FBI agents as Mossad agents. The Israelis were the only suspects arrested anywhere in the United States on 9/11 who were thought to have been involved in the 9/11 attacks.\ \ The two Mossad teams sent regular coded reports on the progress of the 9/11 operation to Tel Aviv via the Israeli embassy in Washington, DC. WMR has learned from a Pentagon source that leading Americans tied to the media effort to pin 9/11 on Arab hijackers, Osama Bin Laden, and the Taliban were present in the Israeli embassy on September 10, 2001, to coordinate their media blitz for the subsequent days and weeks following the attacks. It is more than likely that FBI counter-intelligence agents who conduct surveillance of the Israeli embassy have proof on the presence of the Americans present at the embassy on September 10. Some of the Americans are well-known to U.S. cable news television audiences.\ \ In mid-August, the Mossad team running the Hamburg cell in Boston reported to Tel Aviv that the final plans for 9/11 were set. The Florida-based Mossad cell reported that the documented "presence" of the Arab cell members at Florida flight schools had been established.\ \ The two Mossad cells studiously avoided any mention of the World Trade Center or targets in Washington, DC in their coded messages to Tel Aviv. Halevy covered his tracks by reporting to the CIA of a "general threat" by an attack by Arab terrorists on a nuclear plant somewhere on the East Coast of the United States. CIA director George Tenet dismissed the Halevy warning as "too non-specific." The FBI, under soon-to-be-departed director Louis Freeh, received the "non-specific" warning about an attack on a nuclear power plant and sent out the information in its routine bulletins to field agents but no high alert was ordered.\ \ The lack of a paper trail pointing to "Al Qaeda" as the masterminds on 9/11, which could then be linked to Al Qaeda's Mossad handlers, threw off the FBI. On April 19, 2002, FBI director Robert Mueller, in a speech to San Francisco's Commonwealth Club, stated: "In our investigation, we have not uncovered a single piece of paper — either here in the United States, or in the treasure trove of information that has turned up in Afghanistan and elsewhere — that mentioned any aspect of the September 11 plot."\ \ The two Mossad "Al Qaeda" infiltration and control teams had also helped set up safe houses for the quick exfiltration of Mossad agents from the United States. Last March, WMR reported: "WMR has learned from two El Al sources who worked for the Israeli airline at New York’s John F. Kennedy airport that on 9/11, hours after the Federal Aviation Administration (FAA) grounded all civilian domestic and international incoming and outgoing flights to and from the United States, a full El Al Boeing 747 took off from JFK bound for Tel Aviv’s Ben Gurion International Airport. The two El Al employee sources are not Israeli nationals but legal immigrants from Ecuador who were working in the United States for the airline. The flight departed JFK at 4:11 pm and its departure was, according to the El Al sources, authorized by the direct intervention of the U.S. Department of Defense. U.S. military officials were on the scene at JFK and were personally involved with the airport and air traffic control authorities to clear the flight for take-off. According to the 9/11 Commission report, Transportation Secretary Norman Mineta ordered all civilian flights to be grounded at 9:45 am on September 11." WMR has learned from British intelligence sources that the six-man Mossad team was listed on the El Al flight manifest as El Al employees.\ \ WMR previously reported that the Mossad cell operating in the Jersey City-Weehawken area of New Jersey through Urban Moving Systems was suspected by some in the FBI and CIA of being involved in moving explosives into the World Trade Center as well as staging "false flag" demonstrations at least two locations in north Jersey: Liberty State Park and an apartment complex in Jersey City as the first plane hit the World Trade Center's North Tower. One team of Urban Moving Systems Mossad agents was arrested later on September 11 and jailed for five months at the Metropolitan Detention Center in Brooklyn. Some of their names turned up in a joint CIA-FBI database as known Mossad agents, along with the owner of Urban Moving Systems, Dominik Suter, whose name also appeared on a "Law Enforcement Sensitive" FBI 9/11 suspects list, along with the names of key "hijackers," including Mohammed Atta and Hani Hanjour, as well as the so-called "20th hijacker," Zacarias Moussaoui.\ \ Suter was allowed to escape the United States after the FBI made initial contact with him at the Urban Moving Systems warehouse in Weehawken, New Jersey, following the 9/11 attacks. Suter was later permitted to return to the United States where he was involved in the aircraft parts supply business in southern Florida, according to an informe3d source who contacted WMR. Suter later filed for bankruptcy in Florida for Urban Moving Systems and other businesses he operated: Suburban Moving & Storage Inc.; Max Movers, Inc.; Invsupport; Woodflooring Warehouse Corp.; One Stop Cleaning LLC; and City Carpet Upholstery, Inc. At the time of the bankruptcy filing in Florida, Suter listed his address as 1867 Fox Court, Wellington, FL 33414, with a phone number of 561 204-2359.\ \ From the list of creditors it can be determined that Suter had been operating in the United States since 1993, the year of the first attack on the World Trade Center. In 1993, Suter began racking up American Express credit card charges totaling $21,913.97. Suter also maintained credit card accounts with HSBC Bank and Orchard Bank c/o HSBC Card Services of Salinas, California, among other banks. Suter also did business with the Jewish Community Center of Greater Palm Beach in Florida and Ryder Trucks in Miami. Miami and southern Florida were major operating areas for cells of Israeli Mossad agents masquerading as "art students," who were living and working near some of the identified future Arab "hijackers" in the months preceding 9/11.\ \ ABC's 20/20 correspondent John Miller ensured that the Israeli connection to "Al Qaeda's" Arab hijackers was buried in an "investigation" of the movers' activities on 9/11. Anchor Barbara Walters helped Miller in putting a lid on the story about the movers and Suter aired on June 21, 2002. Miller then went on to become the FBI public affairs spokesman to ensure that Mueller and other FBI officials kept to the "Al Qaeda" script as determined by the Bush administration and the future 9/11 Commission. But former CIA chief of counter-terrorism Vince Cannistraro let slip to ABC an important clue to the operations of the Mossad movers in New Jersey when he stated that the Mossad agents "set up or exploited for the purpose of launching an intelligence operation against radical Islamists in the area, particularly in the New Jersey-New York area." The "intelligence operation" turned out to have been the actual 9/11 attacks. And it was no coincidence that it was ABC's John Miller who conducted a May 1998 rare interview of Osama Bin Laden at his camp in Afghanistan. Bin Laden played his part well for future scenes in the fictional "made-for-TV" drama known as 9/11.\ \ WMR has also learned from Italian intelligence sources that Mossad's running of "Al Qaeda" operatives did not end with running the "hijacking" teams in the United States and Hamburg. Other Arab "Al Qaeda" operatives, run by Mossad, were infiltrated into Syria but arrested by Syrian intelligence. Syria was unsuccessful in turning them to participate in intelligence operations in Lebanon. Detailed information on Bin Laden's support team was offered to the Bush administration, up to days prior to 9/11, by Gutbi al-Mahdi, the head of the Sudanese Mukhabarat intelligence service. The intelligence was rejected by the Biush White House. It was later reported that Sudanese members of "Al Qaeda's" support network were double agents for Mossad who had also established close contacts with Yemeni President Ali Abdullah Saleh and operated in Egypt, Saudi Arabia, and Eritrea, as well as Sudan. The Mossad connection to Al Qaeda in Sudan was likely known by the Sudanese Mukhabarat, a reason for the rejection of its intelligence on "Al Qaeda" by the thoroughly-Mossad penetrated Bush White House. Yemen had also identified "Al Qaeda" members who were also Mossad agents. A former chief of Mossad revealed to this editor in 2002 that Yemeni-born Mossad "deep insertion" commandos spotted Bin Laden in the Hadhramaut region of eastern Yemen after his escape from Tora Bora in Afghanistan, following the U.S. invasion.\ \ French intelligence determined that other Egyptian- and Yemeni-born Jewish Mossad agents were infiltrated into Sharjah in the United Arab Emirates as radical members of the Muslim Brotherhood. However, the "Muslim Brotherhood" agents actually were involved in providing covert Israeli funding for "Al Qaeda" activities. On February 21, 2006, WMR reported on the U.S. Treasury Secretary's firing by President Bush over information discovered on the shady "Al Qaeda" accounts in the United Arab Emirates: "Banking insiders in Dubai report that in March 2002, U.S. Secretary of Treasury Paul O’Neill visited Dubai and asked for documents on a $109,500 money transfer from Dubai to a joint account held by hijackers Mohammed Atta and Marwan al Shehhi at Sun Trust Bank in Florida. O'Neill also asked UAE authorities to close down accounts used by Al Qaeda . . . . The UAE complained about O’Neill’s demands to the Bush administration. O’Neill’s pressure on the UAE and Saudis contributed to Bush firing him as Treasury Secretary in December 2002 " O'Neill may have also stumbled on the "Muslim Brotherhood" Mossad operatives operating in the emirates who were directing funds to "Al Qaeda."\ \ After the collapse of the Soviet Union and the rise to power of the Taliban in Afghanistan, Sharjah's ruler, Sultan bin Mohammed al-Qasimi, who survived a palace coup attempt in 1987, opened his potentate to Russian businessmen like Viktor Bout, as well as to financiers of radical Muslim groups, including the Taliban and "Al Qaeda."\ \ Moreover, this Israeli support for "Al Qaeda" was fully known to Saudi intelligence, which approved of it in order to avoid compromising Riyadh. The joint Israeli-Saudi support for "Al Qaeda" was well-known to the Sharjah and Ras al Khaimah-based aviation network of the now-imprisoned Russian, Viktor Bout, jailed in New York on terrorism charges. The presence of Bout in New York, a hotbed of Israeli intelligence control of U.S. federal prosecutors, judges, as well as the news media, is no accident: Bout knows enough about the Mossad activities in Sharjah in support of the Taliban and Al Qaeda in Afghanistan, where Bout also had aviation and logistics contracts, to expose Mossad as the actual mastermind behind 9/11. Bout's aviation empire also extended to Miami and Dallas, two areas that were nexuses for the Mossad control operations for the "Al Qaeda" flight training operations of the Arab cell members in the months prior to 9/11.\ \ Bout's path also crossed with "Al Qaeda's" support network at the same bank in Sharjah, HSBC. Mossad's phony Muslim Brotherhood members from Egypt and Yemen controlled financing for "Al Qaeda" through the HSBC accounts in Sharjah. Mossad's Dominik Suter also dealt with HSBC in the United States. The FBI's chief counter-terrorism agent investigating Al Qaeda, John O'Neill, became aware of the "unique" funding mechanisms for Al Qaeda. It was no mistake that O'Neill was given the job as director of security for the World Trade Center on the eve of the attack. O'Neill perished in the collapse of the complex.Mossad uses a number of Jews born in Arab countries to masquerade as Arabs. They often carry forged or stolen passports from Arab countries or nations in Europe that have large Arab immigrant populations, particularly Germany, France, Britain, Denmark, Sweden, and the Netherlands.\ \ For Mossad, the successful 9/11 terrorist "false flag" operation was a success beyond expectations. The Bush administration, backed by the Blair government, attacked and occupied Iraq, deposing Saddam Hussein, and turned up pressure on Israel's other adversaries, including Iran, Syria, Pakistan, Hamas, and Lebanese Hezbollah. The Israelis also saw the U.S., Britain, and the UN begin to crack down on the Lebanese Shi'a diamond business in Democratic Republic of Congo and West Africa, and with it, the logistics support provided by Bout's aviation companies, which resulted in a free hand for Tel Aviv to move in on Lebanese diamond deals in central and west Africa.\ \ Then-Israeli Finance Minister Binyamin Netanyahu commented on the 9/11 attacks on U.S. television shortly after they occurred. Netanyahu said: "It is very good!" It now appears that Netanyahu, in his zeal, blew Mossad's cover as the masterminds of 9/11.\ \ Wayne Madsen is a Washington, DC-based investigative journalist, author and syndicated columnist. He has written for several renowned papers and blogs.\ \ Madsen is a regular contributor on Russia Today. He has been a frequent political and national security commentator on Fox News and has also appeared on ABC, NBC, CBS, PBS, CNN, BBC, Al Jazeera, and MS-NBC. Madsen has taken on Bill O’Reilly and Sean Hannity on their television shows. He has been invited to testifty as a witness before the US House of Representatives, the UN Criminal Tribunal for Rwanda, and an terrorism investigation panel of the French government.\ \ As a U.S. Naval Officer, he managed one of the first computer security programs for the U.S. Navy. He subsequently worked for the National Security Agency, the Naval Data Automation Command, Department of State, RCA Corporation, and Computer Sciences Corporation.\ \ Madsen is a member of the Society of Professional Journalists (SPJ), Association for Intelligence Officers (AFIO), and the National Press Club. He is a regular contributor to Opinion Maker
-
 @ 0e9491aa:ef2adadf
2025-05-23 14:01:30
@ 0e9491aa:ef2adadf
2025-05-23 14:01:30
Nostr is an open communication protocol that can be used to send messages across a distributed set of relays in a censorship resistant and robust way.
If you missed my nostr introduction post you can find it here. My nostr account can be found here.
We are nearly at the point that if something interesting is posted on a centralized social platform it will usually be posted by someone to nostr.
We are nearly at the point that if something interesting is posted exclusively to nostr it is cross posted by someone to various centralized social platforms.
We are nearly at the point that you can recommend a cross platform app that users can install and easily onboard without additional guides or resources.
As companies continue to build walls around their centralized platforms nostr posts will be the easiest to cross reference and verify - as companies continue to censor their users nostr is the best censorship resistant alternative - gradually then suddenly nostr will become the standard. 🫡
Current Nostr Stats
If you found this post helpful support my work with bitcoin.

-
 @ 25f5c1c7:e956c514
2025-05-22 23:42:09
@ 25f5c1c7:e956c514
2025-05-22 23:42:09I've been exploring ways to retain the strong security guarantees of Proof-of-Work (PoW) while significantly reducing its environmental footprint. Traditional PoW systems are undeniably robust, but their energy demands are a major concern. Delayed Proof-of-Work (DPoW) is my first proposal toward solving this - a concept designed to preserve the integrity and fairness of PoW while operating with a fraction of the hash power.
How it Works
-
A new block is added to the chain.
-
All miners start computing a VDF (Verifiable Delay Function) with the latest block's hash as the input.
-
The VDF is designed to take 4 minutes to complete, enforcing a mandatory idle period.
-
The \~1 minute mining period begins when miners complete the VDF.
-
- Miners compete to find a valid PoW for a new block, which includes the VDF output in the header.
-
The first miner to find a valid hash broadcasts the new block to the network.
-
The block is verified by nodes by checking the VDF's output is correct for the previous block hash, and that the PoW is valid.
-
This cycle of a 4 minute idle period and a brief mining period continues.
Key Advantages
-
The idle-mine cycle allows the network to operate with \~1/5 of the hash power of a standard PoW blockchain while still taking advantage of the security properties of PoW.
-
During the 4 minute idle period, the blockchain is guaranteed to be static. The predictable delay means blocks are propagated and confirmed in a more synchronised fashion, which could reduce synchronisation issues and orphaned blocks.
Potential Issues
-
VDFs can be computed slightly faster on hardware with higher clock speeds or specialised circuits, resulting in some miners having a longer mining period.
-
The short mining-window means that miners on faster connections will have a significant advantage over slower connections, as they will be able to propagate a mined block faster.
-
The VDF also uses energy, although negligible compared to the amount that algorithms use.
-
Miners might redirect their hash power to other cryptocurrencies during the delay period, which would undermine the goal of reducing energy consumption.
-
A malicious miner who obtains or predicts the next block could start pre-computing the VDF early, gaining an unfair advantage.
-
-
 @ 0e9491aa:ef2adadf
2025-05-23 14:01:30
@ 0e9491aa:ef2adadf
2025-05-23 14:01:30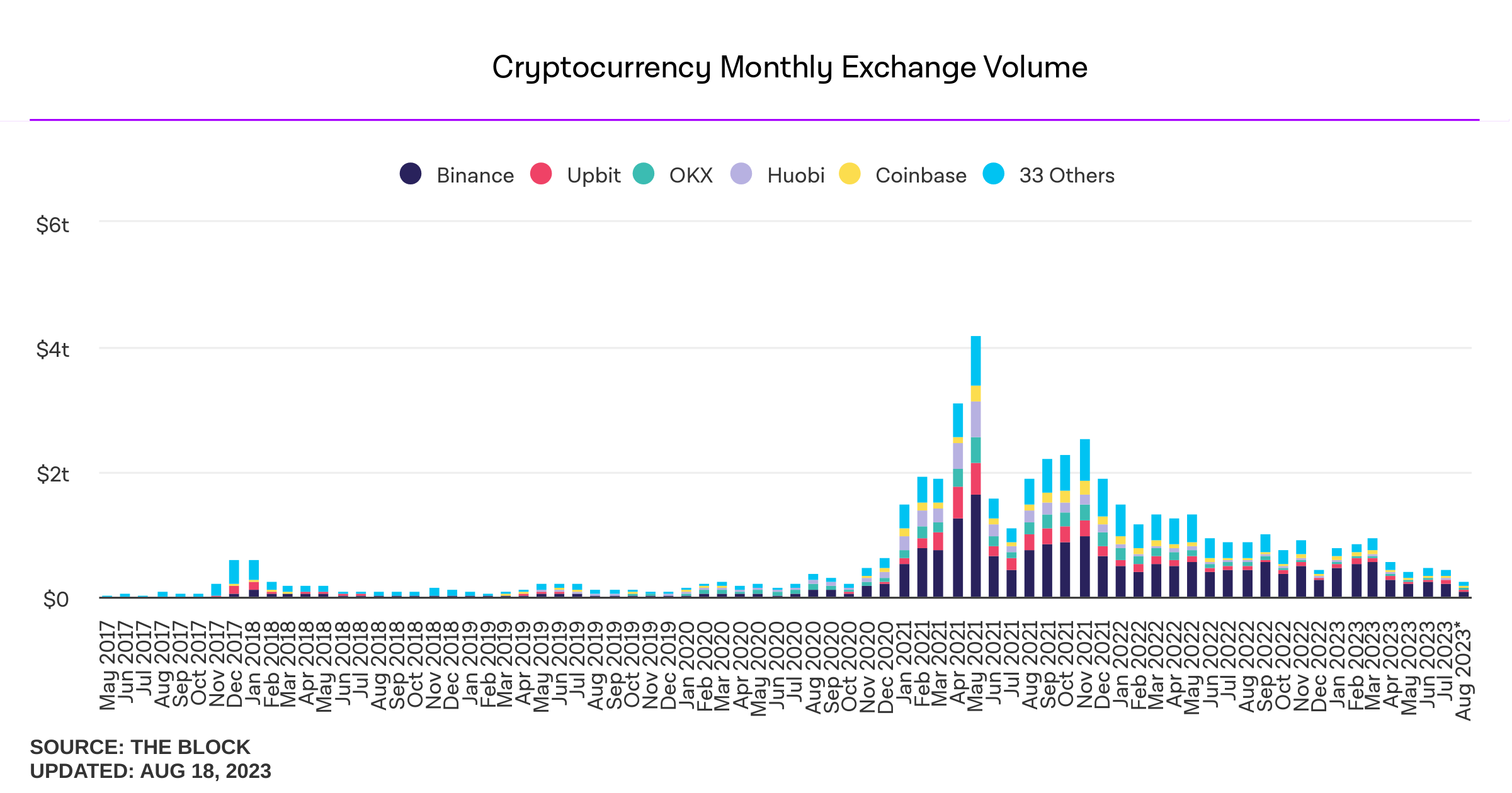
Influencers would have you believe there is an ongoing binance bank run but bitcoin wallet data says otherwise.
- binance wallets are near all time highs
- bitfinex wallets are also trending up
- gemini and coinbase are being hit with massive withdrawals thoughYou should not trust custodians, they can rug you without warning. It is incredibly important you learn how to hold bitcoin yourself, but also consider not blindly trusting influencers with a ref link to shill you.
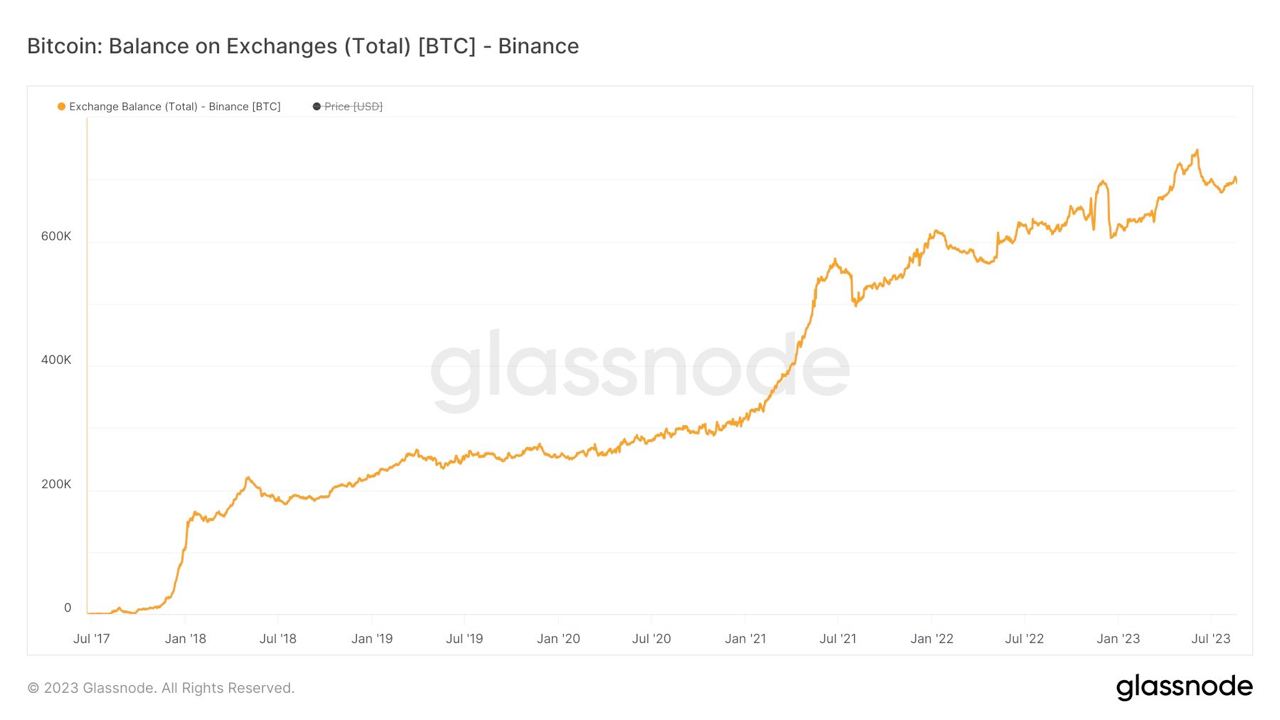
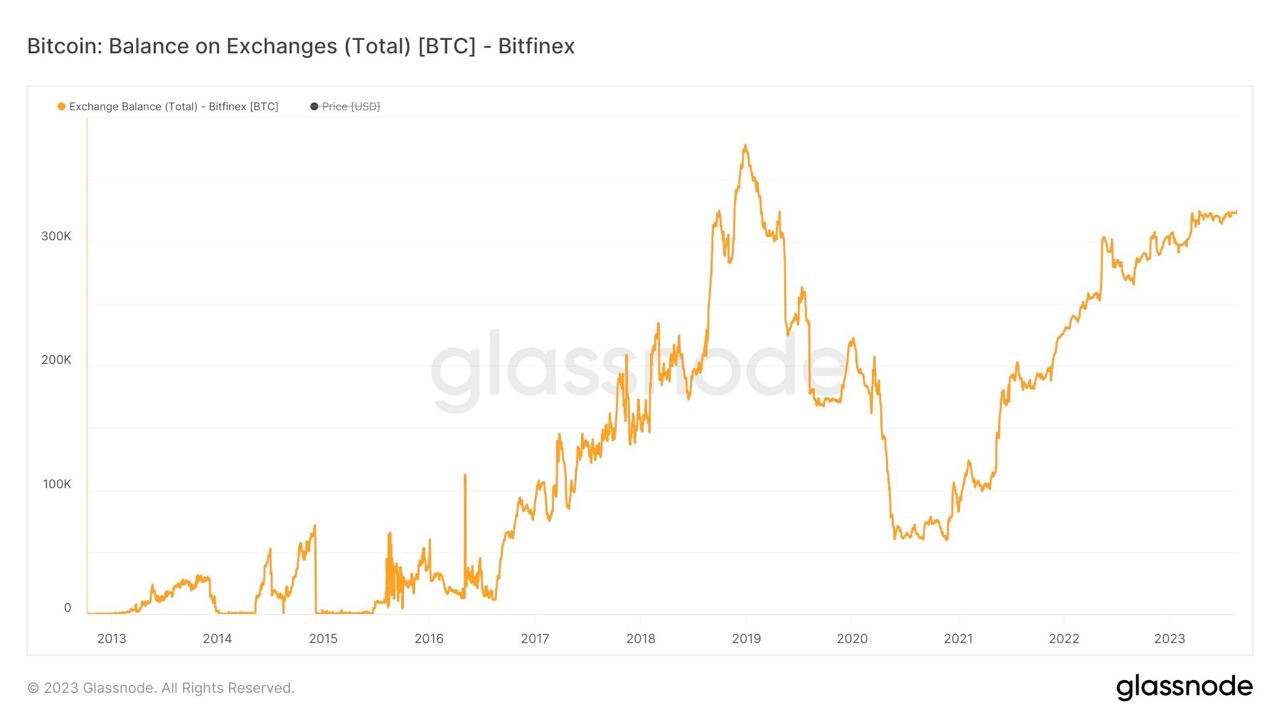
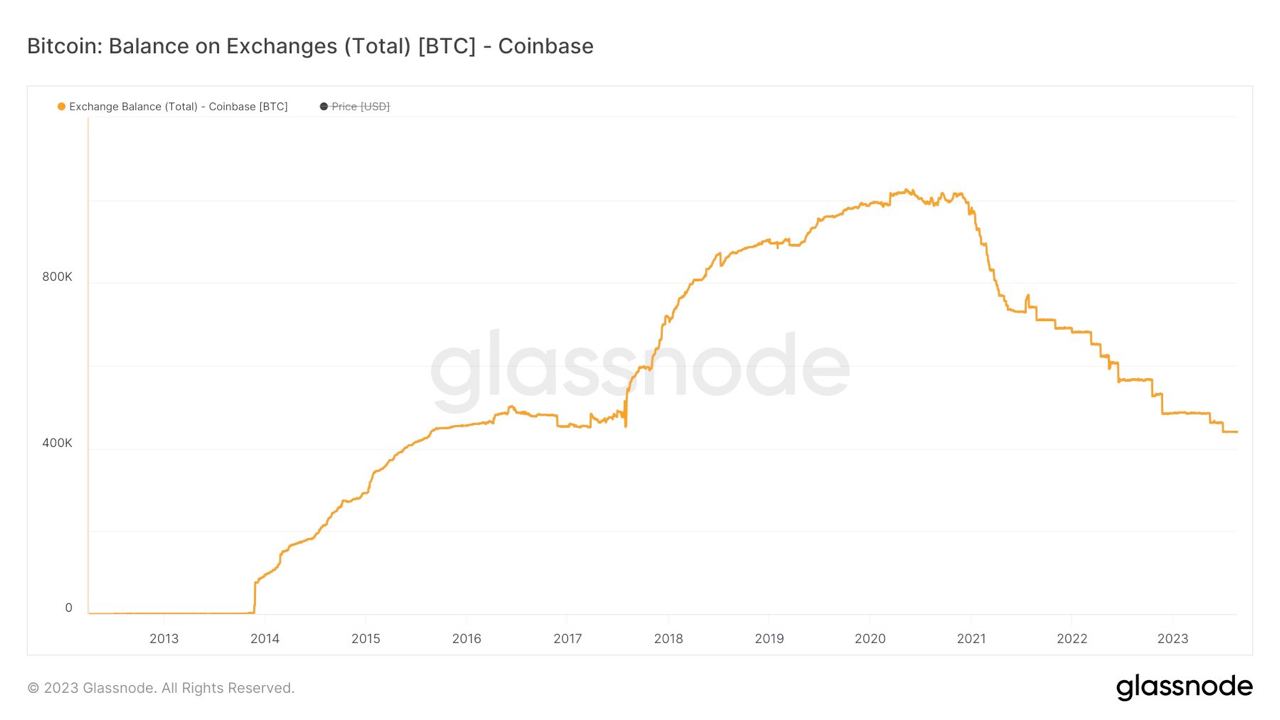

If you found this post helpful support my work with bitcoin.

-
 @ 1817b617:715fb372
2025-05-22 23:39:18
@ 1817b617:715fb372
2025-05-22 23:39:18🚀 Instantly Send Spendable Flash BTC, ETH, & USDT — 100% Blockchain-Verifiable!
Step into the future of cryptocurrency innovation with CryptoFlashingTool.com — your go-to solution for sending spendable Flash Bitcoin (BTC), Ethereum (ETH), and USDT transactions. Using cutting-edge 🔥 Race/Finney-style blockchain simulation, our technology generates coins that are virtually indistinguishable from real, fully confirmed blockchain transactions. Transactions stay live and spendable from 60 up to 360 days!
🌐 Explore all the details at cryptoflashingtool.com.
🌟 Why Trust Our Crypto Flashing System? Whether you’re a blockchain enthusiast, ethical hacker, security expert, or digital entrepreneur, our solution offers a perfect mix of authenticity, speed, and flexibility.
🎯 Top Features You’ll Love: ✅ Instant Blockchain Simulation: Transactions are complete with valid wallet addresses, transaction IDs, and real confirmations.
🔒 Privacy First: Works flawlessly with VPNs, TOR, and proxies to keep you fully anonymous.
🖥️ User-Friendly Software: Built for Windows, beginner and pro-friendly with simple step-by-step guidance.
📅 Flexible Flash Durations: Choose how long coins stay valid — from 60 to 360 days.
🔄 Full Wallet Compatibility: Instantly flash coins to SegWit, Legacy, or BCH32 wallets with ease.
💱 Exchange-Ready: Spend your flashed coins on leading exchanges like Kraken and Huobi.
📊 Proven Results: ✅ Over 79 billion flash transactions completed. ✅ 3000+ satisfied users around the globe. ✅ 42 active blockchain nodes ensuring fast, seamless performance.
📌 How It Works: Step 1️⃣: Input Transaction Info
Pick your coin (BTC, ETH, USDT: TRC-20, ERC-20, BEP-20). Set amount and flash duration. Enter the recipient wallet (auto-validated). Step 2️⃣: Make Payment
Pay in your selected crypto. Scan the QR code or use the provided address. Upload your transaction proof (hash and screenshot). Step 3️⃣: Launch the Flash
Blockchain confirmation simulation happens instantly. Your transaction appears real within seconds. Step 4️⃣: Verify & Spend
Access your flashed coins immediately. Verify your transactions using blockchain explorers. 🛡️ Why Our Flashing Tech Leads the Market: 🔗 Race/Finney Attack Mechanics: Mimics authentic blockchain behavior. 🖥️ Private iNode Clusters: Deliver fast syncing and reliable confirmation. ⏰ Live Timer: Ensures fresh, legitimate transactions. 🔍 Real Blockchain TX IDs: All transactions come with verifiable IDs.
❓ FAQs:
Is flashing secure? ✅ Yes, fully encrypted with VPN/proxy compatibility. Multiple devices? ✅ Yes, up to 5 Windows PCs per license. Chargebacks possible? ❌ No, flashing is irreversible. Spendability? ✅ Flash coins stay spendable 60–360 days. Verification after expiry? ❌ No, transactions expire after the set time. Support? ✅ 24/7 Telegram and WhatsApp help available. 🔐 Independent, Transparent, Trusted:
At CryptoFlashingTool.com, we pride ourselves on unmatched transparency, speed, and reliability. See our excellent reviews on ScamAdvisor and top crypto forums!
📲 Contact Us: 📞 WhatsApp: +1 770 666 2531 ✈️ Telegram: @cryptoflashingtool
🎉 Ready to Flash Like a Pro?
💰 Buy Flash Coins Now 🖥️ Get Your Flashing Software
The safest, smartest, and most powerful crypto flashing solution is here — only at CryptoFlashingTool.com!
Instantly Send Spendable Flash BTC, ETH, & USDT — 100% Blockchain-Verifiable!
Step into the future of cryptocurrency innovation with CryptoFlashingTool.com — your go-to solution for sending spendable Flash Bitcoin (BTC), Ethereum (ETH), and USDT transactions. Using cutting-edge
Race/Finney-style blockchain simulation, our technology generates coins that are virtually indistinguishable from real, fully confirmed blockchain transactions. Transactions stay live and spendable from 60 up to 360 days!
Explore all the details at cryptoflashingtool.com.
Why Trust Our Crypto Flashing System? Whether you’re a blockchain enthusiast, ethical hacker, security expert, or digital entrepreneur, our solution offers a perfect mix of authenticity, speed, and flexibility.
Top Features You’ll Love:
Instant Blockchain Simulation: Transactions are complete with valid wallet addresses, transaction IDs, and real confirmations.
Privacy First: Works flawlessly with VPNs, TOR, and proxies to keep you fully anonymous.
User-Friendly Software: Built for Windows, beginner and pro-friendly with simple step-by-step guidance.
Flexible Flash Durations: Choose how long coins stay valid — from 60 to 360 days.
Full Wallet Compatibility: Instantly flash coins to SegWit, Legacy, or BCH32 wallets with ease.
Exchange-Ready: Spend your flashed coins on leading exchanges like Kraken and Huobi.
Proven Results:
Over 79 billion flash transactions completed.
3000+ satisfied users around the globe.
42 active blockchain nodes ensuring fast, seamless performance.
How It Works: Step
: Input Transaction Info
- Pick your coin (BTC, ETH, USDT: TRC-20, ERC-20, BEP-20).
- Set amount and flash duration.
- Enter the recipient wallet (auto-validated).
Step
: Make Payment
- Pay in your selected crypto.
- Scan the QR code or use the provided address.
- Upload your transaction proof (hash and screenshot).
Step
: Launch the Flash
- Blockchain confirmation simulation happens instantly.
- Your transaction appears real within seconds.
Step
: Verify & Spend
- Access your flashed coins immediately.
- Verify your transactions using blockchain explorers.
Why Our Flashing Tech Leads the Market:
Race/Finney Attack Mechanics: Mimics authentic blockchain behavior.
Private iNode Clusters: Deliver fast syncing and reliable confirmation.
Live Timer: Ensures fresh, legitimate transactions.
Real Blockchain TX IDs: All transactions come with verifiable IDs.
FAQs:
- Is flashing secure?
Yes, fully encrypted with VPN/proxy compatibility. - Multiple devices?
Yes, up to 5 Windows PCs per license. - Chargebacks possible?
No, flashing is irreversible. - Spendability?
Flash coins stay spendable 60–360 days. - Verification after expiry?
No, transactions expire after the set time. - Support?
24/7 Telegram and WhatsApp help available.
Independent, Transparent, Trusted:
At CryptoFlashingTool.com, we pride ourselves on unmatched transparency, speed, and reliability. See our excellent reviews on ScamAdvisor and top crypto forums!
Contact Us:
WhatsApp: +1 770 666 2531
Telegram: @cryptoflashingtool
Ready to Flash Like a Pro?
The safest, smartest, and most powerful crypto flashing solution is here — only at CryptoFlashingTool.com!
-
 @ 0e9491aa:ef2adadf
2025-05-23 14:01:30
@ 0e9491aa:ef2adadf
2025-05-23 14:01:30
For years American bitcoin miners have argued for more efficient and free energy markets. It benefits everyone if our energy infrastructure is as efficient and robust as possible. Unfortunately, broken incentives have led to increased regulation throughout the sector, incentivizing less efficient energy sources such as solar and wind at the detriment of more efficient alternatives.
The result has been less reliable energy infrastructure for all Americans and increased energy costs across the board. This naturally has a direct impact on bitcoin miners: increased energy costs make them less competitive globally.
Bitcoin mining represents a global energy market that does not require permission to participate. Anyone can plug a mining computer into power and internet to get paid the current dynamic market price for their work in bitcoin. Using cellphone or satellite internet, these mines can be located anywhere in the world, sourcing the cheapest power available.
Absent of regulation, bitcoin mining naturally incentivizes the build out of highly efficient and robust energy infrastructure. Unfortunately that world does not exist and burdensome regulations remain the biggest threat for US based mining businesses. Jurisdictional arbitrage gives miners the option of moving to a friendlier country but that naturally comes with its own costs.
Enter AI. With the rapid development and release of AI tools comes the requirement of running massive datacenters for their models. Major tech companies are scrambling to secure machines, rack space, and cheap energy to run full suites of AI enabled tools and services. The most valuable and powerful tech companies in America have stumbled into an accidental alliance with bitcoin miners: THE NEED FOR CHEAP AND RELIABLE ENERGY.
Our government is corrupt. Money talks. These companies will push for energy freedom and it will greatly benefit us all.
Microsoft Cloud hiring to "implement global small modular reactor and microreactor" strategy to power data centers: https://www.datacenterdynamics.com/en/news/microsoft-cloud-hiring-to-implement-global-small-modular-reactor-and-microreactor-strategy-to-power-data-centers/
If you found this post helpful support my work with bitcoin.

-
 @ bf47c19e:c3d2573b
2025-05-22 21:03:52
@ bf47c19e:c3d2573b
2025-05-22 21:03:52Originalni tekst na bitcoin-balkan.com.
Pregled sadržaja
- Šta je finansijski samo-suverenitet?
- Zašto smo prestali da koristimo zlatni standard?
- Šta fali tradicionalnoj valuti i centralnim bankama?
- Kako mogu ljudi da mi ukradu novac ako je u banci?
- Kako ljudi koriste moje finansijske podatke protiv mene?
- Kako ljudi kontrolišu sa kim obavljam transakcije?
- Kako da povratimo svoj finansijski samo-suverenitet?
- Kako Bitcoin funkcioniše?
- Pa onda, zašto Bitcoin?
- Po čemu je Bitcoin bolji od sistema tradicionalnih valuta?
- Kako Bitcoin štiti od Inflacije?
- Kako Bitcoin štiti od Zaplene?
- Kako Bitcoin štiti Privatnost?
- Kako Bitcoin štiti od Cenzure?
- Šta će vlada i banke učiniti sa Bitcoin-om?
- Da li je vrednost Bitcoin-a nestabilna?
- Da li je Bitcoin novac?
- Bitcoin kao Zaliha Vrednosti
- Bitcoin kao Sredstvo Razmene
- Bitcoin kao Obračunska Jedinica
- Bitcoin kao Sistem Kontrole
- Šta je sa „Sledećim Bitcoin-om“?
- Na kraju
Kratki uvod u bezbednost, privatnost i slobodu vašeg novca.
Pre nego što saznate kako morate znati zašto.
Šta je finansijski samo-suverenitet?
Zamislite da u ruci imate zlatni novčić, jedan od najjednostavnijih i najčistijih oblika finansijskog samo-suvereniteta.
Da biste držali taj zlatni novčić, ne morate da se složite sa bilo kojim Uslovima korišćenja ili Politikom privatnosti, da se pridržavate bilo kojih KYC ili AML propisa, da pokažete ličnu kartu, da navedete svoje ime ili jedinstveni matični broj.
Samo ga držite u ruci i njime možete platiti bilo šta, davanjem tog novčića nekom drugom da ga drži u ruci. To je čista sloboda.
Pored slobode onoga što kupujete svojim novčićem, niko ne može magično znati kome plaćate ili koju robu/usluge kupujete tim zlatni novčićem, jer vaša privatnost nije ugrožena sa zlatom.
A pošto imate svoju privatnost, niko ne može znati za vaše transakcije, pa niko ne može da odluči da ograniči ili kontroliše za šta koristite taj zlatni novčić.
Hiljadama godina zlato je bilo globalni standard novca.
Svi su održavali svoj finansijski samo-suverenitet, a privatnost i sloboda svačijeg novca su poštovani.
Zaista je bilo tako jednostavno.
Zašto smo prestali da koristimo zlatni standard?
Trenutni globalni bankarski sistem i sistem tradicionalnih valuta, bankari su vrlo polako implementirali u proteklih 100+ godina.
Udružili su se sa svetskim vladama koje su svima oduzele zlato pod pretnjom nasilja.
Na primer, nakon što je Federalna banka rezervi osnovana u SAD-u 1913. godine, američka vlada je nasilno oduzela svo zlato 1933. godine, prisiljavajući sve da koriste nove centralne banke i sistem novčanica Federalnih rezervi.
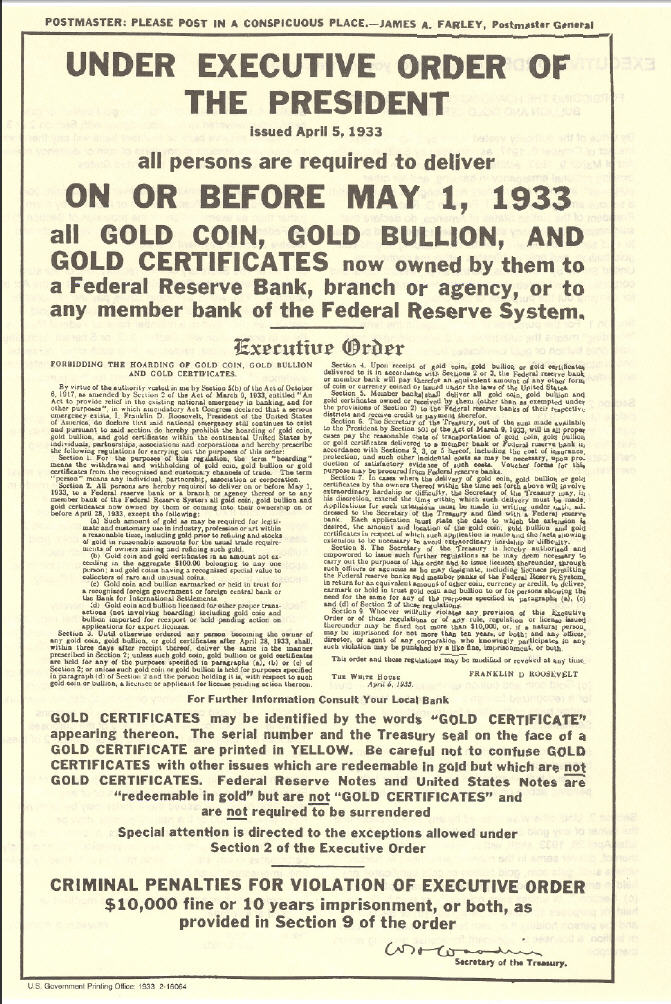 „Dostavite svoje celokupno zlato u naše sefove u zamenu za bezvredni papir, ili ćemo upotrebiti silu nad vama.“
„Dostavite svoje celokupno zlato u naše sefove u zamenu za bezvredni papir, ili ćemo upotrebiti silu nad vama.“Banke su u početku zamenile zlatni standard papirnim priznanicama zvane zlatni sertifikati, ali nakon što je prošlo dovoljno vremena, banke su u osnovi jednostavno prestale da ih otkupljuju za zlato.
Zlatni sertifikati izdavani od banaka (novčanice ili „gotovina“) u tom trenutku bili su samo bezvredni papir, ali zbog vladine pretnje nasiljem, svi su bili primorani da nastave da koriste novčanice Federalnih rezervi.
Od skora, banke koriste digitalnu bazu podataka, u kojoj doslovno mogu stvoriti novac ni iz čega, čak i da ga ne moraju štampati na papiru.
Predsednik Federalnih rezervi priča kako oni „štampaju“ novac.
Oni su učvrstili svoju moć da manipulišu i naduvaju globalnu novčanu masu, nadgledaju finansijske transakcije svih i kontrolišu protok svih tradicionalnih valuta u svom bankarskom sistemu.
Banke sada kontrolišu sve.
Jednom kada su centralni bankari uspešno preuzeli kontrolu nad novčanom masom u svetu, zajedno sa sposobnošću svih da slobodno vrše transakcije i trguju, svet je kolektivno izgubio bezbednost, slobodu i privatnost svog novca.
Šta fali tradicionalnoj valuti i centralnim bankama?
Nakon impelentacije trenutnog globalnog bankarskog sistema i sistema tradicionalnih valuta, svetu nije preostao drugi izbor nego da veruje bankarima i političarima da vode globalni finansijski sistem na pošten način.
„Koren problema tradicionalne valute je potpuno poverenje potrebno za njeno funkcionisanje. Centralnoj banci se mora verovati da neće devalvirati valutu, ali istorija tradicionalnih valuta je puna kršenja tog poverenja. Bankama se mora verovati da čuvaju naš novac i prenose ga elektronskim putem, ali ga daju u talasima kreditnih balona sa malim delićem rezerve. ““ — Satoshi Nakamoto
Istorija zloupotrebe tradicionalnih valuta može se grupisati u 3 kategorije:
• Bezbednost. Loši ljudi kradu vaš novac ili vrednost vašeg novca, ponekad na očigledne načine, ponekad na podle načine.
• Privatnost. Loši ljudi nadgledaju sve vaše privatne finansijske transakcije, i koriste vaše lične finansijske podatke protiv vas.
• Sloboda. Loši ljudi kontrolišu na koji način možete da trošite sopstveni novac, sa kim možete da obavljate transakcije, koliko možete da potrošite itd.
Kako mogu ljudi da mi ukradu novac ako je u banci?
Evo nekoliko primera:
-
Krađa inflacijom: Ovo je primarni način na koji banke kradu vaš novac i jedan od najpodlijih. Kada centralne banke izdaju novi novac, bilo štampanjem na bezvrednom papiru, ili samo dodavanjem knjigovodstvenog unosa u bazu podataka koju kontrolišu, one naduvaju globalnu novčanu masu. Inflacija krade kupovnu moć svih koji drže deo te valute, jednostavno zato što je sada više te valute u opticaju. Zlato se ne može stvoriti, pa su bankari umesto toga izmislili sistem papirnog novca.
-
Krađa zaplenom: Ovo je jedan od načina na koji vlade mogu ukrasti vaš novac. Da li ste ikada čuli za zaplenu imovine? Ako policajac posumnja da je vaša imovina korišćena u krivičnom delu, može je zapleniti, a vi se morate boriti da biste povratili vašu ukradenu imovinu. Ili, drugi primer: Pokušajte da uđete u zemlju sa više od 10.000 USD u džepu, a ne da je prijavite, i pogledajte šta će se dogoditi. Sve je isto: krađa od strane drugih ljudi sa oružjem.
-
Krađa putem oporezivanja: Ovo je još jedan način na koji vam vlade kradu novac. Ne sporim da li je oporezivanje etično ili ne, samo konstatujem činjenicu da vaša vlada može da primora vašu banku da im da vaš novac, a ovo je bezbednostna ranjivost. Da bi novac bio siguran, mora biti nezaplenjiv, a vlade mogu da zaplene vaše bankovne račune.
Kako ljudi koriste moje finansijske podatke protiv mene?
Ako fizičku tradicionalnu valutu predate drugoj osobi, u obliku papirnog novca ili kovanica, relativno je lako zaštititi privatnost svoje transakcije, baš kao što bi bilo da koristite zlatnike.
Međutim, ako koristite kreditne kartice, debitne kartice, bankovne transfere, PayPal, Venmo, LINE Pay, WeChat Pay ili bilo koju drugu mrežu za plaćanje koja je centralno kontrolisana, aktivno pristajete da se odreknete privatnosti podataka svih svojih privatnih finansijskih transakcija i sve ih dajete poverljivoj trećoj strani.
Kada su svi podaci i metapodaci vaših finansijskih transakcija prijavljeni u centralnu bazu podataka, onaj ko ima pristup toj bazi podataka može da koristi vaše podatke protiv vas.
Evo nekoliko osnovnih primera:
- Ako ste kupili robu rizičnog životnog stila poput cigareta, banka može reći vašoj osiguravajućoj kompaniji da poveća vaše osiguranje.
- Ako ste kupili nešto što je ilegalno, poput droga za rekreaciju, vaša banka može reći vašoj vladi da vas zakonski goni.
Ali u slučaju nekih represivnih vlada, oni su to odveli do ekstrema. Oni centralno prikupljaju sve finansijske transakcije i druge podatke svih svojih građana i stvorili su totalitarni Sistem Socijalnih Bodova (eng. Social Credit Score):
 Prepoznavanje lica je jedan od elemenata kineskih napora za praćenje
Prepoznavanje lica je jedan od elemenata kineskih napora za praćenjeZapisi George Orwell-a već su postali stvarnost u Kini zbog sistema tradicionalnih valuta centralne banke i platnih mreža koje su izgrađene na njemu.
Ako mislite da se to neće dogoditi u vašoj zemlji, razmislite ponovo.
To se dešava vrlo polako, ali na kraju će sve svetske vlade primeniti Sistem Socijalnih Bodova, dok je Kina to tek prva učinila.
Kako ljudi kontrolišu sa kim obavljam transakcije?
U prvom primeru sa zlatnim novčićem, kada ga predate nekom drugom kao plaćanje za robu ili uslugu, ne postoji centralizovana evidencija vaše platne transakcije i imate savršenu privatnost.
Međutim, u centralnom bankarskom sistemu, budući da banka ima i znanje o podacima o vašim transakcijama i moć da kontroliše vaša sredstva, oni mogu proceniti niz pravila da bi odlučili da li žele da dozvole vašu transakciju ili da to odbiju, takođe kao i izvršenje te odluke kontrolišući vaša sredstva.
Tako su vlade naoružale tradicionalne valute i centralni bankarski sistem kao Sistem Kontrole nad svojim građanima.
Da rezimiramo: Pošto ste se odrekli bezbednosti i privatnosti svog novca, izgubili ste i svoju finansijsku slobodu.
“Privatnost nije o tome da nešto treba sakriti. Privatnost je o tome da nešto treba zaštititi.” — Edward Snowden
Kako da povratimo svoj finansijski samo-suverenitet?
Pokret Cypherpunk pokrenuli su pojedinci koji su shvatili važnost zaštite privatnosti i slobode pojedinačnih korisnika na Internetu.
Cypherpunk-ovi su verovali da se gore opisani problemi mogu rešiti samo potpuno novim novčanim sistemom, koji poštuje i štiti bezbednost, privatnost i slobodu pojedinca.
Mnogi od Cypherpunk-era pokušali su da izgrade nove etičke sisteme e-gotovine koji bi mogli da zamene tradicionalne valute i centralno bankarstvo.
Bilo je mnogo teških računarskih problema koje je trebalo prevazići u stvaranju tako istinski decentralizovanog sistema, i ako su neki od njih bili blizu cilja, svi su propali.
Odnosno, sve dok jedan pseudonim Cypherpunk-a to konačno nije shvatio 2008. godine: kombinacijom digitalnih potpisa, distribuirane knjige i peer-to-peer mreže, rođen je Bitcoin.
Kako Bitcoin funkcioniše?
Baš kao što ne treba da znate kako Internet funkcioniše da bi gledali slike mačaka na Internetu, razumevanje tehničke složenosti načina na koji Bitcoin radi „ispod haube“ nije neophodno da biste ga koristili i postigli sopstveni finansijski samo-suverenitet.
Važna stvar koju želim da saznate iz ovog članka je da iako većina novih tehnologija u početku ima loše korisničko iskustvo, Bitcoin svesno i vrlo namerno ne žrtvuje svoje osnovne filozofske principe da bi brže pridobio nove korisnike, ili da bi poboljšao korisničko iskustvo.
Najpametniji Cypherpunk-ovi rade na poboljšanju korisničkog iskustva.
Tehnologija će se sa vremenom poboljšavati, baš kao i za Internet.
Pa onda, zašto Bitcoin?
Reći ću vam zašto:
Jer Bitcoin poštuje bezbednost, privatnost i slobodu pojedinca.
Po čemu je Bitcoin bolji od sistema tradicionalnih valuta?
Za početak, Bitcoin nema Uslove korišćenja, Politiku privatnosti i Propise o usklađenosti sa KYC/AML. (Know Your Costumer & Anti-money Laundering)
Bitcoin je uspešan primer implementacije kripto-anarhije, gde su jedina pravila kriptografija, matematika i jak skup konsenzusnih pravila.
To je distribuirani i nepoverljivi sistem zasnovan na finansijskim podsticajima i nijedna osoba ili centralizovani entitet ne može da kontroliše Bitcoin.
Ono što je najvažnije, Bitcoin vam omogućava da odustanete od tradicionalnih valuta, sistema delimičnih rezervi i centralnog bankarstva rešavanjem osnovnih problema poverenja:
- Sigurnost od inflacije korišćenjem fiksnog snabdevanja
- Sigurnost od zaplene korišćenjem ključeva za kontrolu sredstava
- Privatnost plaćanja korišćenjem pseudonimnih identiteta
- Sloboda protiv cenzure korišćenjem peer to peer mreže
Kako Bitcoin štiti od Inflacije?
Jedno od najkritičnijih pravila konsenzusa o Bitcoin-u je da može postojati najviše 21,000,000 Bitcoin-a.
Nakon izdavanja svih Bitcoin-a, nikada više ne može doći do stvaranja novih Bitcoin-a.
Stoga je Bitcoin deflaciona valuta, koja sprečava ljude da ukradu vaš novac ili njegovu vrednost naduvavanjem novčane mase.
 Monetarna Inflacija Bitcoin-a
Monetarna Inflacija Bitcoin-aKako Bitcoin štiti od Zaplene?
Bitcoin se može preneti samo pomoću kriptografskog privatnog ključa koji kontroliše sredstva.
Nijedan bitcoin nikada ne izadje van sistema.
Nijedna vlada, banka ili sudski nalog ne mogu zapleniti ta sredstva.
Jednostavno ne postoji način da se takva odredba ili naredba sprovede od bilo kog „organa vlasti“, jer Bitcoin ne priznaje nijedno „ovlašćenje“ u svom sistemu.
Bitcoin je potpuno samo-suveren sistem i zbog svoje distribuirane prirode ne može se ugasiti.
Postoji zbog sopstvenih zasluga, samo zato što ljudi veruju u to.
Kako Bitcoin štiti Privatnost?
Bitcoin ne traži vaše ime ili druge detalje koji mogu lično da vas identifikuju.
Vaš identitet je kriptografski, a ne vaše stvarno ime.
Dakle, vaš identitet izgleda otprilike kao 1vizSAISbuiKsbt9d8JV8itm5ackk2TorC, a ne kao „Stefan Petrovič“.
Pored toga, niko ne zna ko kontroliše sredstva na datoj Bitcoin adresi, a nova tehnologija se neprestano razvija kako bi se poboljšala privatnost Bitcoin-a.
Kako Bitcoin štiti od Cenzure?
Peer-to-peer Bitcoin mreža je u potpunosti distribuirana.
To znači da ako jedan čvor pokuša da cenzuriše vašu transakciju, neće uspeti ukoliko * svaki * čvor(Node) ne izvrši cenzuru vaše transakcije.
Šta će vlada i banke učiniti sa Bitcoin-om?
Neke zemlje su pokušale da ga regulišu, kontrolišu, isključe itd., ali nijedna od njih nije uspela.
Čini se da uglavnom samo žele da koriste postojeći sistem centralnih banaka da bi kontrolisali kako ljudi trguju tradicionalnim valutama za Bitcoin, i naravno žele da oporezuju Bitcoin na bilo koji mogući način.
Evo nekoliko uobičajenih tvrdnji vlada i banaka o Bitcoin-u:
 Evropska centralna banka kaže da Bitcoin nije valuta i upozorava da je vrlo nestabilna.
Evropska centralna banka kaže da Bitcoin nije valuta i upozorava da je vrlo nestabilna.„Bitcoin, izgleda samo kao prevara“, rekao je gospodin Tramp. „Ne sviđa mi se jer je to još jedna valuta koja se takmiči sa dolarom.“
Da li je vrednost Bitcoin-a nestabilna?
Ako umanjite grafikon cena, videćete da Bitcoin-u neprekidno raste vrednost od kada je stvoren, trgujući sa manje od 0,01 USD i polako se penje na preko 60.000 USD na nedavnom vrhuncu početkom 2021. godine.
 Cena Bitcoina od 2011. godine
Cena Bitcoina od 2011. godineTo je zato što je njegova ponuda fiksna i ljudi cene njegovu nestašicu.
Sa većom potražnjom i fiksnom ponudom, cene vremenom rastu.
Kako godine odmiču, njegova vrednost će se povećavati kako novi korisnici počinju da drže Bitcoin. (U svetu Bitcoina držanju kažemo HODL. Drži bitcoin. Hodl bitcoin.)
Da li je Bitcoin novac?
Da biste odgovorili na pitanje da li je Bitcoin novac ili ne, prvo morate definisati pojam „novac“.
Nažalost, reč „novac“ koristimo da bismo opisali nekoliko vrlo različitih komplikovanih koncepata, koji su svi potpuno odvojeni.
Termin „novac“ se zapravo odnosi na:
- Zaliha Vrednosti (Store of Value)
- Sredstvo Razmene ( Medium of Exchange)
- Obračunska Jedinica (Unit of Account)
- Sistem Kontrole (System Control)
Bitcoin kao Zaliha Vrednosti
Ovaj tweet to savršeno objašnjava:
Sinov prijatelj: “Matt, šta će se dogoditi ako novčić od 1 funte usitnite na pola?”
Dobijaš dva komada bezvrednog metala. Ako zlatnik usitnite na pola, dobićete dva zlatnika, od kojih svaki vredi polovinu onoga što je novčić bio.
Sin: „… isto tako kao sa zlatom jeste sa bitcoinima“.
Bitcoin je potpuno deljiv i deluje kao izvrsna zaliha vrednosti, baš kao što je i zlato već hiljadama godina.
Bitcoin kao Sredstvo Razmene
Bitcoin je dobro služio kao sredstvo razmene za svoje rane korisnike.
Ali skaliranje Bitcoin-a na globalni nivo koji bi mogao da posluži svim ljudima je veliki izazov, jer se osnovna „blockchain“ tehnologija ne skalira na globalni nivo.
Da bi rešio ovaj problem skaliranja, Satoshi je izumeo koncept kanala plaćanja, a u kombinaciji sa malo pomoći drugih briljantnih računarskih naučnika Cipherpunk-a koji su poboljšali koncept tokom poslednjih 10 godina, sada imamo mrežu Lightning, koja omogućava da se Bitcoin koristi kao odlično Sredstvo Razmene, koje se vremenom može proširiti na globalni nivo.
Bitcoin kao Obračunska Jedinica
Najmanja obračunska jedinica Bitcoin-a nazvana je po njenom tvorcu, Satoshi-u.
Jedan Bitcoin je jednak 100.000.000 Satoshi-a.
Na kraju, kako se robe i usluge sve češće razmenjuju za Bitcoin, sve više ljudi će koristiti Bitcoin ili „Sats“ kao obračunsku jedinicu.
Bitcoin kao Sistem Kontrole
Budući da je Bitcoin dizajniran da poštuje i štiti ljudska prava pojedinca, posebno bezbednost, privatnost i slobodu novca; ne bi bio dobar Sistem Kontrole i ne može se koristiti za ugnjetavanje ljudi, kao što se dešava sa tradicionalnim valutama i sistemima centralnog bankarstva koji to trenutno vrlo dobro rade.
Šta je sa „Sledećim Bitcoin-om“?
Kao što može biti samo jedan „globalni“ Internet, tako može biti i samo jedan globalni novac, a stigao je i novi Bitcoin Standard.
Sve ostalo je ili direktna prevara ili gubljenje vremena.
Ako bi neko želeo da vam proda „Sledeće Zlato“, da li biste ga kupili?
Na kraju
Nadam se da vam je ovaj članak pomogao da razumete zašto je Bitcoin stvoren i kako može da pomogne svetu da se oslobodi tradicionalnih valuta i sistema centralnog bankarstva koji je veoma duboko integrisan u naše trenutno društvo.
Evo nekoliko misli koje treba poneti sa sobom:
- Bitcoin nije izmišljen radi zarade, već je izmišljen da bi promenio svet.
- Bitcoin će to učiniti poštujući korisnikovu bezbednost, privatnost i slobodu.
- Bitcoin se već koristi kao novac, na nekoliko načina na koji se novac može koristiti.
- Bitcoin nije nestabilan, njegova vrednost vremenom polako raste (odzumirajte).
- Bitcoin ima mnogo kopija i prevaranata koji će pokušati da vam prodaju svoju kopiju Bitcoin-a. Ne zavaravajte se lažnim Bitcoin-om baš kao što vas ne bi prevarili ni Lažnim Zlatom.
- Bitcoin će postati najveći prenos bogatstva u našem životu, tako da ćete možda želeti da ih uzmete pre nego kasnije.
- Ostanite skromni i skupljajte satošije.
-
 @ 000002de:c05780a7
2025-05-22 20:50:21
@ 000002de:c05780a7
2025-05-22 20:50:21I'm mostly curious about how Tapper can do this with a straight face.
https://stacker.news/items/986926
-
 @ 99e7936f:d5d2197c
2025-05-23 13:51:11
@ 99e7936f:d5d2197c
2025-05-23 13:51:11Staugefahr
Manchmal ist der Lehrer interessanter als der Unterrichtsinhalt. Man lernt dann beiläufig, obwohl das Thema öde ist. Mir ging das vor vielen Jahren so, als ich in meiner Ausbildung zur Krankenschwester Inhalte zum Thema Hygiene lernen durfte. Unser Lehrer für Hygiene duschte morgens in der Schule, bevor er uns unterrichtete, damit er, sauber vor uns sitzend, glaubwürdig über die permanente Gefahr der Mikroorganismen im Klinikalltag reden konnte. Er lebte das, was er predigte. Er bot pathogenen Keimen keinen Nährboden. Er pflegte sich und seine Kleidung penibel. Er trug Hosen, Pullover und Schuhe aus den 70ern, die kaum Gebrauchsspuren aufwiesen. Er blieb Überzeugungen, die er einmal für richtig befunden hatte, treu, war aber stets bereit, etwas Neues anzunehmen, wenn dies Sinn machte. Bevor er jedoch Neues annahm, prüfte er mehrfach gründlich, las Fachliteratur und vermied Gespräche mit Experten.
Er versuchte damals, Entscheidungsträger in der Klinik darüber aufzuklären, wie man mit einfachen Mitteln Infektionen im Hause hätte minimieren können. Meist wurden seine Vorschläge nur zögerlich umgesetzt, obwohl seine Argumente fachlich richtig waren.
Mir kommt es heute mit dem Thema „Trauma“ und „traumatisierte Gesellschaft“ ähnlich vor. Niemand möchte sich mit dem Thema beschäftigen, obwohl doch alle wissen müssten, dass viele unangenehme Verhaltensweisen von Menschen im Alltag oder in der Politik etwas mit diesem Thema zu tun haben. Aber das Thema scheint irgendwie unbequem, mühsam und, vor allem, nicht greifbar.
Ein Trauma kann man genau so wenig sehen wie einen pathogenen Keim, deswegen scheint die Auseinandersetzung mit diesem Thema wie eine unappetitliche und lästige Pflichtaufgabe, die man nur mit spitzen Fingern anfasst, wenn überhaupt.
Wie kann man dieses dringend zu besprechende Thema „Trauma“ sichtbar machen?
Vielleicht geht das mit dem Bild vom Stau auf der Autobahn. Den kennt jeder. Und den Stau kann man nicht übersehen. Große leuchtende Schilder weisen auf ihn hin, damit man nicht unvorbereitet in ihn hinein fährt. Überall wird vor dem Stau gewarnt. Und trotzdem passiert er, denn wir sind der Stau, wir selbst machen den Stau.
Stau passiert, weil es Hindernisse auf unserem Weg gibt.
Der Stau ist VOR dem Hindernis. Die Traumafolgen sind gewissermaßen der Stau in unserem Leben, obwohl das Trauma HINTER uns liegt. Wie geht das? Ein Trauma liegt zeitlich gesehen zwar in der Vergangenheit, aber energetisch gesehen liegt es immer vor uns. Es begleitet uns, verfolgt uns, holt uns ein. Energie kennt kein VOR oder HINTER. Energie ist allgegenwärtig. Sobald das Trauma integriert ist, hört dieser Spuk auf. Aber ein nicht bearbeitetes Trauma stellt definitiv ein Hindernis auf unserem (Lebens)Weg dar. Es liegt dann VOR uns.
Dieser Vergleich humpelt ein wenig, zeigt aber dennoch die einfachen Mechanismen von Trauma auf, wie ich finde.
Auf der Autobahn gibt es also ein Hindernis. Entweder gibt es eine bekannte Baustelle, die wir bereits beim Planen der Route zur Kenntnis genommen haben (Trauma ist bereits gut bekannt). Oder es gibt einen Unfall auf der Strecke vor uns, den niemand absehen konnte (Das frühe Trauma wird in einer Alltagssituation plötzlich aktiviert). Jedenfalls stehen wir dann geplant oder ungeplant im Stau, vielmehr sind wir der Stau. Es geht nur langsam oder gar nicht mehr weiter, obwohl der (Lebens)Motor läuft. Bei Trauma ist das auch so. Trauma bewirkt ganz viel Entwicklungsverzögerung in einzelnen Lebensbereichen. Menschen erlernen mehrere Berufe, brauchen länger, um beruflich anzukommen, heiraten später, mehrfach oder nie. Menschen mit Trauma haben manchmal auch beruflich wie privat große Erfolge, fallen dann aber tief, um dadurch letztlich neu geboren zu werden. Trauma sieht man nicht immer auf den ersten Blick. Es kann auch hinter jeder normalen Fassade stecken. Je nach Schwere des Traumas, kann Trauma auch alle Lebensbereiche gleichermaßen treffen. Das entspricht dann dem Pendler, der regelmäßig Sommer wie Winter im Stau steht und auch schon selbst mal eine Panne, im Stau stehend, hatte.
Man erreicht einfach nicht die Ziele, die man sich selbst gesteckt hat. Man kann dann versuchen, die nächste Abfahrt zu nehmen, einen Umweg zu fahren, während des Staus etwas anderes zu erledigen, sich selbst zu erzählen, dass ein Stau gar kein Hindernis sei, sondern eine prima Gelegenheit, um eine Pause zu machen. Und man kann andere Menschen anrufen und erklären, dass man später komme oder sonstiges tun. Aber man steht im Stau, man ist der Stau. Es geht nicht so weiter, wie gewünscht, und man muss das hinnehmen. Verschiedene unangenehme Gefühle melden sich zwangsläufig. Man stellt sich die Sinnfrage, man schaut, wie andere mit dem Stau umgehen, und man möchte gefühlt nie wieder in einem Stau stehen, weil es nervt. Es bringt einen nicht um, aber es nervt. Und es ist ja nicht das erste Mal. Man möchte so gern ein Leben haben ohne Stau. Das wär´s. Es nervt einfach. Und dann nach langer Zeit, mit Blick auf die Tankanzeige, geht es endlich weiter. Die Autos fahren langsam an und der Verkehr rollt wieder. Man wirft einen kurzen Blick auf das Verkehrshindernis und fährt dann zügig weiter. Denn man will nur noch weg von diesem Streckenabschnitt/ Lebensabschnitt. Der Stresspegel im Körper geht runter, man atmet durch und entspannt sich. Aber es war unschön. Nächstes Mal will man die Route besser planen oder gleich mit dem Zug fahren. Man ist erleichtert und hat endlich die Kontrolle über sein Leben zurück. Jetzt ist alles möglich.
Es gibt viele Parallelen zwischen einem Stau und einem Trauma bzw. den Traumafolgen.
Traumabewältigung ist jedoch viel schmerzhafter, als an einem Verkehrshindernis nach längerer Wartezeit einfach vorbei zu fahren. Und man verpasst auch mehr im Leben als nur eine Stunde Zeit, die man auf leblosem Asphalt verbringt. Der Preis, den man für Trauma bezahlt, ist kaum zu beziffern. Und ein Trauma wirft nicht nur die Sinnfrage auf, sondern auch die Frage nach der eigenen Identität. Im Stau auf der Autobahn weiß ich genau, wer ich bin. Aber nach einem frühen Trauma gehen einige Seelenanteile auf eine lange Reise. Und wenn ein Trauma später im Leben passiert, dann sagen Menschen: „Ich habe mich selbst nicht mehr wieder erkannt.“ Trauma wirbelt alles in Dir durcheinander. Und genau darin liegt die Chance. Du musst jedes Teil, jeden Aspekt Deiner Persönlichkeit einzeln in die Hand nehmen, an den richtigen Ort zurück legen, und dadurch lernst Du Dich selbst kennen (und lieben) wie nie zuvor. Der Gewinn von Traumaarbeit übersteigt den zuvor gezahlten Preis. Das nennt man dann posttraumatisches Wachstum. Man ist erleichtert und hat viel mehr als nur die Kontrolle über sein Leben zurück. Eigentlich ist das schon die ganze Geschichte.
Das riesige Problem an der Traumabewältigung ist halt, dass es ein so schmerzhafter und langwieriger Prozess ist. Aber auch hier gibt es gute Nachrichten. Viel von dem Kummer, den wir „im Stau“ erleben, hat etwas mit unseren positiv wie negativ übertriebenen Erwartungen an uns und andere und dem verloren gegangenen Kulturwissen in Bezug auf das Thema „Trauma“ zu tun. Trauma hat die Eigenart, in Vergessenheit zu geraten. Daher gibt es viele falsche Verkehrsmeldungen diesbezüglich. Deswegen möchte ich mein Erfahrungswissen zum Thema „Trauma“ teilen, weil ich denke, dass das Ängste abbauen kann, sich diesem Thema auf ganz natürliche Weise anzunähern, vergleichbar mit der WDR-Produktion „der siebte Sinn“ und getreu dem Motto „Gefahr erkannt, Gefahr gebannt“.
Man kann jedes Problem aufbauschen oder sachlich betrachten. Und es macht einen riesigen Unterschied, ob man mit einem Problem allein gelassen wird, oder ob man wohlwollende und kundige Hilfe an der Seite hat. Und genau dies sind meine zentralen Kritikpunkte zum Thema. Das Thema „Trauma“ wird als unlösbar hingestellt und dadurch unnötig aufgebauscht. Deswegen muss man dieses Thema quasi schon vermeiden, wenn man sich nicht den Tag verderben möchte. Und in der Folge werden von Experten Hilfen angepriesen, die aber leider oft nicht zuverlässig helfen können, weil das Thema ja unlösbar ist. Der verhängnisvolle Kreis schließt sich, und man kommt ins Schleudern.
Kulturwissen wird verfälscht und verdreht, ein übles Schleudertrauma entsteht.
Nein, mal im Ernst, ich möchte das Thema sachlich betrachten und zumindest Impulse für eine günstige Betrachtungsweise geben. Diese Impulse kommen aus meinen persönlichen Erfahrungen und aus Beobachtungen, die ich gemacht habe. Mir ist bewusst, dass jeder Mensch Verletzungen und spätere Probleme, die daraus resultieren, unterschiedlich erlebt. Aber vielleicht geht es gerade um diesen in unserer Kultur fehlenden analogen, lebendigen und authentischen Austausch von Nicht-Experten über die verschiedenen Verletzungen, die daraus resultierende Probleme und die - sehr wohl - vorhandenen Lösungen.
Trauma ist das, was man draus macht.
Ich persönlich kenne niemanden, der kein Trauma erlebt hat.
Leben bedeutet immer auch, dass man Verletzungen erlebt.
Trauma passiert jedem.
Trauma passiert auch robusten Menschen.
Bestimmte Traumata haben immer sehr ähnliche Traumafolgen. Man ist nicht alleine damit.
Menschen reagieren ähnlich auf bestimmte Ereignisse im Leben, das hängt mit unserem Menschsein, der Biologie und der Evolution zusammen.
Menschen reden nicht gern über ihr Trauma.
Menschen schämen sich für ihr Trauma.
Menschen geben sich selbst die Schuld für ihr Trauma.
Menschen versuchen alles, um ihr Trauma zu vergessen oder ungeschehen zu machen.
Menschen erleben einen tiefen Schmerz durch Trauma.
Menschen werden aggressiv, weil sie selber verletzt wurden.
Menschen werden durch Aggression selbst zum Täter. Diese Gefahr besteht zumindest.
Menschen lehnen sich selbst ab für diese aggressiven Impulse.
Alle Gefühle haben eine Funktion. Auch negative Gefühle haben eine Funktion.
Negative Gefühle beschützen unser Leben.
Deswegen sind auch negative Gefühle im bestimmten Maße gut.
Der Schmerz, der durch Trauma entsteht, hat jedoch eine besondere Funktion.
Streng genommen, ist er kein Gefühl, aber egal.
Er ist jedenfalls der letzte und wichtigste Hüter des Lebens. Man sollte ihn nicht übergehen oder versuchen, ihn weg zu machen. Er ist die rote Ampel, die den Stau regelt.
Eine rote Ampel in einem Stau zu ignorieren, ist verhängnisvoll.
Halte lieber an dieser roten Ampel im Stau, auch wenn es schmerzt.
Dieser Schmerz ist die schwierigste, aber auch wichtigste Herausforderung bei der Traumabewältigung, denn er verzögert Dein ohnehin gestautes Leben noch zusätzlich.
Wer es schafft, die Geduld aufzubringen und sich diesem Schmerz hinzugeben, der erlebt Wunder.
Dieses schlimmste Gefühl bringt Dir quasi Dein Leben und die grüne Welle zurück.
Wenn der Schmerz zu Dir kommt, dann heiße ihn willkommen.
Wir sind gesellschaftlich betrachtet mit unseren unguten Verhaltensweisen mittlerweile im Stau angekommen, und die Ampel, die den Stau regelt, steht auf Rot.
Je ehrlicher wir den Schmerz jetzt zulassen, spüren und nicht wegmachen, desto eher sind wir bereit, unbequeme Veränderungen, die vielleicht mit Verzicht, Orientierungslosigkeit und zaghaften Versuchen zu tun haben, zu beginnen. Im Schmerz wächst ein Bewusstsein dafür, was richtig ist. Und es wächst die Kraft, das Gute zu tun. Der Schmerz macht entschlossen. Der Schmerz zeigt, wo das Lebendige liegt und dass es schützenswert ist. Der Schmerz reduziert unseren Blick auf das Wesentliche, auf das Leben und die Liebe, was aufs Gleiche heraus kommt. Der Schmerz markiert einfach nur die Grenze des Lebens. Und deswegen ist er gut, besonders in diesen Tagen.
Heiße den Schmerz willkommen, er gibt uns alle Information FÜR das Leben.
-
 @ 7e6f9018:a6bbbce5
2025-05-22 18:17:57
@ 7e6f9018:a6bbbce5
2025-05-22 18:17:57Governments and the press often publish data on the population’s knowledge of Catalan. However, this data only represents one stage in the linguistic process and does not accurately reflect the state of the language, since a language only has a future if it is used. Knowledge is a necessary step toward using a language, but it is not the final stage — that stage is actual use.
So what is the state of Catalan usage? If we look at data on regular use, we see that the Catalan language has remained stagnant over the past hundred years, with nearly the same number of regular speakers. In 1930, there were around 2.5 million speakers, and in 2018, there were 2.7 million.
 Regular use of Catalan in Catalonia, in millions of speakers. The dotted segments are an estimate of the trend, based on the statements of Joan Coromines and adjusted according to Catalonia’s population growth.
Regular use of Catalan in Catalonia, in millions of speakers. The dotted segments are an estimate of the trend, based on the statements of Joan Coromines and adjusted according to Catalonia’s population growth.These figures wouldn’t necessarily be negative if the language’s integrity were strong, that is, if its existence weren’t threatened by other languages. But the population of Catalonia has grown from 2.7 million in 1930 to 7.5 million in 2018. This means that today, regular Catalan speakers make up only 36% of Catalonia’s population, whereas in 1930, they represented 90%.
 Regular use of Catalan in Catalonia, as a percentage of speakers. The dotted segments are an estimate of the trend, based on the statements of Joan Coromines and adjusted according to Catalonia’s population growth.
Regular use of Catalan in Catalonia, as a percentage of speakers. The dotted segments are an estimate of the trend, based on the statements of Joan Coromines and adjusted according to Catalonia’s population growth.The language that has gained the most ground is mainly Spanish, which went from 200,000 speakers in 1930 to 3.8 million in 2018. Moreover, speakers of other foreign languages (500,000 speakers) have also grown more than Catalan speakers over the past hundred years.
Notes, Sources, and Methodology
The data from 2003 onward is taken from Idescat (source). Before 2003, there are no official statistics, but we can make interpretations based on historical evidence. The data prior to 2003 is calculated based on two key pieces of evidence:
-
1st Interpretation: In 1930, 90% of the population of Catalonia spoke Catalan regularly. Source and evidence: The Romance linguist Joan Coromines i Vigneaux, a renowned 20th-century linguist, stated in his 1950 work "El que s'ha de saber de la llengua catalana" that "In this territory [Greater Catalonia], almost the entire population speaks Catalan as their usual language" (1, 2).\ While "almost the entire population" is not a precise number, we can interpret it quantitatively as somewhere between 80% and 100%. For the sake of a moderate estimate, we assume 90% of the population were regular Catalan speakers, with the remaining 10% being immigrants and officials of the Spanish state.
-
2nd Interpretation: Regarding population growth between 1930 and 1998, on average, 60% is due to immigration (mostly adopting or already using Spanish language), while 40% is natural growth (likely to acquire Catalan language from childhood). Source and evidence: Between 1999 and 2019, when more detailed data is available, immigration accounted for 68% of population growth. From 1930 to 1998, there was a comparable wave of migration, especially between 1953 and 1973, largely of Spanish-speaking origin (3, 4, 5, 6). To maintain a moderate estimate, we assume 60% of population growth during that period was due to immigration, with the ratio varying depending on whether the period experienced more or less total growth.
-
-
 @ f1989a96:bcaaf2c1
2025-05-22 17:09:23
@ f1989a96:bcaaf2c1
2025-05-22 17:09:23Good morning, readers!
Today, we begin in China, where the central bank injected $138 billion into the economy and expanded the money supply by 12.5% year-over-year. As the regime eases monetary conditions to prop up a decelerating economy, Chinese citizens are rushing to preserve their savings, evidenced by Bitcoin/CNY trading activity jumping over 20% on the news. But while some escape to harder money, others remain trapped. In Hunan, an elderly Chinese woman died outside a bank after being forced to appear in person in order to withdraw her own money for medical care.\ \ In Central America, Salvadoran President Bukele revived a “foreign agents” bill that would impose a 30% tax on foreign-funded NGOs, threatening to financially crush organizations that hold those in power accountable and protect journalists and civil society. The proposal mirrors laws used in Russia, China, Belarus, and beyond to suppress dissent. And it arrives amid Bukele’s authoritarian drift and increasing threats to independent journalists.\ \ In open-source news, we highlight a new tool called ChapSmart, a Bitcoin-powered remittance service that allows users to send Bitcoin to citizens and families in Tanzania and have it disbursed in Tanzanian shillings (TZS) via M-PESA. This tool is increasingly helpful as the Tanzanian regime tightens control over foreign currency, mandating that all transactions be conducted in TZS. ChapSmart provides an accessible way for nonprofits and dissidents to access value from abroad using Bitcoin.\ \ We end with an Ask Me Anything (AMA) with Bitcoin educator Anita Posch on Stacker News, who shares her thoughts, experiences, and views from her time conducting Bitcoin education in authoritarian regimes in Africa. We also feature an article from Togolese human rights advocate Farida Nabourema, who critiques Nigeria’s new investment act for classifying Bitcoin as a security and for the regulatory hurdles this will impose on the grassroots adoption of freedom tech in the country.
Be sure to tune in next week at 2 p.m. Oslo time on Wednesday, May 28, as the Oslo Freedom Forum’s Freedom Tech track airs on Bitcoin Magazine’s livestream channels, headlined by speakers Ziya Sadr, Abubakr Nur Khalil, Amiti Uttarwar, Calle, Sarah Kreps, Ben Perrin, and many more.
Now, let’s read on!
SUBSCRIBE HERE
GLOBAL NEWS
El Salvador | Bukele Reintroduces Foreign Agents Bill
In El Salvador, President Nayib Bukele revived a controversial “foreign agents” bill that threatens to severely restrict the finances and operations of NGOs. While the bill is not finalized, Bukele shared on X that the proposal would impose a 30% tax on donations to NGOs receiving foreign funding. This punitive financial measure alone would severely restrict Salvadoran organizations that protect independent journalism, advocate for human rights, and hold the government accountable. In neighboring Nicaragua, a similar foreign agents law has enabled the closure of more than 3,500 NGOs. El Salvador’s foreign agents bill arrives alongside other alarming moves, including arrest warrants against El Faro journalists, the arrest of human rights lawyer Ruth López, and the detention of more than 200 Venezuelan migrants under dubious claims of gang affiliation.
China | Injects Billions to Stabilize Economy
The Chinese Communist Party (CCP) has injected $138 billion in liquidity through interest rate cuts and a 0.5% reduction in banks’ reserve requirements, in effect expanding the money supply by 12.5% year-over-year. While the state eases monetary conditions to prop up a fragile system, ordinary citizens are left scrambling to preserve the value of their savings. Bitcoin/CNY trading volumes jumped over 20% in response, as people sought refuge from a weakening yuan. But while some can quietly escape to harder money, others are trapped in a system that treats access to money as a privilege. In Hunan, an elderly woman in a wheelchair died outside a bank after being forced to appear in person to withdraw her own money for medical care. Too weak to pass mandatory facial recognition scans, she collapsed after repeated failed attempts.
World | Authoritarian Regimes Lead CBDC Push, Study Finds
A new international study from the Nottingham Business School, part of Nottingham Trent University in England, set out to understand what is driving countries to pursue central bank digital currencies (CBDCs). Researchers found the answer lies mostly in political motives. Analyzing 68 countries, the report revealed that authoritarian governments are pushing CBDCs most aggressively, using their centralized power to hastily roll out CBDCs that can monitor transactions, restrict the movement of money, and suppress dissent. On the other hand, the report found democracies are moving more cautiously, weighing concerns over privacy, transparency, and public trust. The study also noted a correlation: countries with high levels of perceived corruption are more likely to explore CBDCs, often framing them as tools to fight illicit finance. These findings are consistent with HRF’s research, revealing nearly half the global population lives under an authoritarian regime experimenting with a CBDC.
Thailand | Plans to Issue New “Investment Token”
Thailand’s Ministry of Finance plans to issue 5 billion baht ($151 million) worth of “G-Tokens,” a new digital investment scheme that allows Thais to buy government bonds for as little as 100 baht ($3). Officials claim the project will democratize access to state-backed investments and offer higher returns than traditional bank deposits. But in a country rapidly advancing central bank digital currency (CBDC) infrastructure, this initiative raises apparent concerns. The move closely follows Thailand’s repeated digital cash handouts via a state-run wallet app, which restricts spending, tracks user behavior, and enforces expiration dates on money, all clear hallmarks of a CBDC. Luckily, the Thai government postponed the latest handout, but the infrastructure remains. Framing this project as inclusionary masks the reality: Thailand is building state-run digital systems that give the regime more power over citizens’ savings and spending.
Russia | Outlaws Amnesty International
Russia officially banned Amnesty International, designating it as an “undesirable organization” and criminalizing cooperation with the global human rights group. Russian officials claim Amnesty promotes “Russophobic projects” and undermines national security. This adds to the Kremlin’s assault on dissent, targeting human rights advocates, independent journalists, and civil society in the years since the 2022 full-scale invasion of Ukraine. The designation exposes anyone financially, publicly, or privately supporting Amnesty’s work to prosecution and imprisonment up to five years. With more than 220 organizations now blacklisted, Russia is systematically cutting off avenues for international accountability and isolating Russians from external support.
BITCOIN AND FREEDOM TECH NEWS
ChapSmart | Permissionless Remittances in Tanzania
ChapSmart is a Bitcoin-powered remittance service that allows users to send money to individuals and families in Tanzania while having it disbursed in Tanzanian shillings (TZS) via M-PESA. With ChapSmart, no account is needed: just enter your name, email, and the recipient’s M-Pesa details. Choose how much USD to send, pay in bitcoin via the Lightning Network, and ChapSmart delivers Tanzanian shillings instantly to the recipient's M-Pesa account with zero fees. This tool is especially useful as Tanzania’s regime enacts restrictions on foreign currencies, banning most citizens from quoting prices or accepting payment in anything other than TZS. ChapSmart offers a practical and accessible way for families, nonprofits, and individuals to access value from abroad using Bitcoin, even as the state tries to shut out financial alternatives.
Bitkey | Multisignature for Families Protecting Wealth from State Seizure
Decades ago, Ivy Galindo’s family lost their savings overnight when the Brazilian government froze citizens’ bank accounts to “fight inflation.” That moment shaped her understanding of financial repression and why permissionless tools like Bitcoin are essential. When her parents later chose to start saving in Bitcoin, Ivy knew a wallet with a single private key wasn’t enough, as it can be lost, stolen, or handed over under pressure or coercion from corrupt law enforcement or state officials. Multisignature (multisig) wallets, which require approval from multiple private keys to move funds, offer stronger protection against this loss and coercion and eliminate any single points of failure in a Bitcoin self-custody setup. But multisig setups are often too technical for everyday families. Enter Bitkey. This multisig device offered Ivy’s family a simple, secure way to share custody of their Bitcoin in the face of financial repression. In places where wealth confiscation and frozen bank accounts are a lived reality, multisignature wallets can help families stay in full control of their savings.
Parasite Pool | New Zero-Fee, Lightning Native Bitcoin Mining Pool
Parasite Pool is a new open-source Bitcoin mining pool built for home miners who want to contribute to Bitcoin’s decentralization without relying on the large and centralized mining pools. It charges zero fees and offers Lightning-native payouts with a low 10-satoshi threshold, allowing individuals to earn directly and instantly. Notably, it has a “pleb eat first” reward structure, which allocates 1 BTC to the block finder and splits the remaining 2.125 BTC plus fees among all non-winning participants via Lightning. This favors small-scale miners, who can earn outsized rewards relative to their hashpower, inverting the corporate bias of legacy mining pools. This makes Parasite Pool especially attractive for small scale miners, such as those operating in authoritarian contexts who need to mine discreetly and independently. In turn, these very same miners contribute to the Bitcoin network’s resistance to censorship, regulatory capture, and corporate control, ensuring it remains a tool for freedom and peaceful resistance for those who need it most. Learn more about the mining pool here.
Cake Wallet | Implements Payjoin V2
Cake Wallet, a non-custodial, privacy-focused, and open-source mobile Bitcoin wallet, released version 4.28, bringing Payjoin V2 to its user base. Payjoin is a privacy technique that allows two users to contribute an input to a Bitcoin transaction, breaking the common chain analysis heuristic that assumes a sender owns all inputs. This makes it harder for dictators to trace payments or link the identities of activists or nonprofits. Unlike the original Payjoin, which required both the sender and recipient to be online and operate a Payjoin server, Payjoin v2 removes both barriers and introduces asynchronous transactions and serverless communication. This means users can now conduct private transactions without coordination or technical setup, making private Bitcoin transactions much more accessible and expanding the tools dissidents have to transact in the face of censorship, extortion, and surveillance. HRF is pleased to have sponsored the Payjoin V2 specification with a bounty and is happy to see this functionality now in the wild.
Mi Primer Bitcoin | Receives Grant from startsmall
Mi Primer Bitcoin, a nonprofit organization supporting independent Bitcoin education in Central America, announced that it received a $1 million grant from Jack Dorsey’s startsmall public fund. This support will accelerate Mi Primer Bitcoin’s impartial, community-led, Bitcoin-only education. The initiative has trained tens of thousands of students while supporting over 65 grassroots projects across 35+ countries through its Independent Bitcoin Educators Node Network, pushing financial freedom forward where needed most. The Mi Primer Bitcoin (MPB) team stresses the importance of remaining free from government or corporate influence to preserve the integrity of their mission. As founder John Dennehy puts it, “Education will be captured by whoever funds it… We need to create alternative models for the revolution of Bitcoin education to realize its full potential.” MPB has been adopted by many education initiatives working under authoritarian regimes.
Phoenix Wallet | Introduces Unlimited BOLT 12 Offers and Manual Backup Options
Phoenix Wallet, a mobile Bitcoin Lightning wallet, introduced support for unlimited BOLT 12 offers in its v2.6.0 update, allowing users to generate as many reusable Lightning invoices as they like. These offers, which function like static Bitcoin addresses, remain permanently valid and can now include a custom description and amount — ideal for nonprofits or dissidents who need to receive regular donations discreetly. The update also introduces manual export and import of the payments database on Android, enabling users to securely transfer their payment history to new devices. These updates strengthen Phoenix’s position as one of the most user-friendly and feature-complete non-custodial Lightning wallets. BOLT 12 — once a pipe dream — is now a usable activist tool on popularly accessible mobile wallets.
RECOMMENDED CONTENT
Bitcoin Is Not a Security: Why Nigeria’s New Investment and Security Act Misses the Mark by Farida Nabourema
In this article, Togolese human rights advocate Farida Nabourema critiques Nigeria’s 2025 Investment and Securities Act for classifying Bitcoin as a security. Nabourema argues this approach is flawed, economically damaging, disconnected from the realities of Bitcoin usage and innovation across Africa, and an attempt to constrict a human rights tool. She warns that this regulatory framework risks stifling builders and harming the very communities that Bitcoin is helping in a context of widespread currency devaluations, inflation, and exclusion. Read it here.
Ask Me Anything with Anita Posch on Stacker News
After spending five months traveling through countries like Kenya and Zimbabwe, Bitcoin for Fairness Founder Anita Posch joined Stacker News for an Ask Me Anything (AMA) to discuss her view on Bitcoin adoption across the continent. She highlighted major progress since 2020, noting that several grassroots initiatives she supported have become self-sufficient and are now running their own education programs. Despite persistent challenges, like wallet usability, high on-chain fees, and Bitcoin’s misunderstood reputation, she shared stories of real-life impact, including cross-border remittances using mobile airtime and widespread Lightning use via apps like Tando in Kenya. Read the full conversation here.
If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report here.
Support the newsletter by donating bitcoin to HRF’s Financial Freedom program via BTCPay.\ Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ hrf.org
The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals here.
-
 @ 30b99916:3cc6e3fe
2025-05-23 13:16:37
@ 30b99916:3cc6e3fe
2025-05-23 13:16:37sourcegraph #vibecoding #ai #bitcoin #security
After reading the article Revenge of the junior developer, this inspired me to go take a look at Sourcegraph.com to get a better understanding of all this AI stuff.
The first step was installing the VS Code extension called, Cody which is a coding agent. The Cody features explain the code in a file and review and analyze code did an extremely impressive job with VaultApi and BTCwallet.
VaultApi and BTCwallet are PowerShell scripts that are available from my BTCPAY Server
All of the following output was generated by Cody.
Code Analysis of VaultApi.ps1
The VaultApi.ps1 script is generally well-structured and follows many PowerShell best practices. It has comprehensive documentation, version history, and clear parameter definitions. The suggestions below would further enhance what is already a solid codebase. The author has clearly put significant effort into making the script functional and user-friendly, with good attention to cross-platform compatibility and security considerations.
VaultApi.ps1 Explanation
VaultApi.ps1 is a PowerShell script that helps users interact with HashiCorp Vault, which is a tool for securely storing and managing sensitive information like passwords and API keys.
Purpose of the Code
This script makes it easier to use Vault by providing simple commands to start the Vault server, unlock it (unseal), log in, store secrets, retrieve secrets, and shut down the server. Think of it as a friendly interface that simplifies all the complex operations you would otherwise need to do manually with Vault.
Inputs
The script takes several inputs:
- An
actionparameter that tells the script what operation to perform (like "Start", "Stop", "Kv1Create", "Kv1Read") - A
kvpathparameter that specifies where in Vault to store or retrieve information - A
kvalueparameter for the actual secret value you want to store - A
kvkeyparameter that lets you specify a custom name for your secret - Optional switches like
-Infoto show more detailed information and-Rawto display output directly instead of copying to clipboard
Outputs
Depending on the action performed, the script produces different outputs:
- Text messages in the console showing the status of operations
- Secret values retrieved from Vault (either displayed or copied to clipboard)
- Lists of available secret paths
- Status information about the Vault server
- Backup files of your Vault data
How It Works
The script works by:
- First checking if Vault is installed and running
- Setting up communication with the Vault server using its API address
- Performing the requested action by sending the appropriate commands to Vault
- Processing any responses and displaying results to the user
For example, when you use the "Kv1Create" action, the script:
- Checks if you're logged in
- Verifies the path doesn't already exist
- Formats your data correctly
- Sends a request to Vault to create the new secret
- Shows you the result
Important Logic Flows
Some key processes in the script include:
-
Authentication flow: The script helps you log in using either a token or username/password, then stores your authentication token for future commands.
-
Unsealing process: Vault requires multiple keys to unlock (unseal) it after starting. The script can retrieve these keys from a secure file or prompt you to enter them.
-
Secret management: The script handles creating, reading, updating, and deleting secrets, supporting both single values and multiple key-value pairs at a path.
-
Path management: The script can list all available paths and help you search for specific ones, making it easier to organize and find your secrets.
-
Value generation: When creating or updating secrets, you can use the keyword "setvalue" to automatically generate a random 20-character value, which is then copied to your clipboard.
The script uses a configuration file in your home directory to know how to connect to Vault, and it can optionally use encrypted files to store sensitive information like unlock keys. It communicates with Vault using REST API calls, which are like special messages that tell Vault what to do.
In summary, VaultApi.ps1 is a helper tool that makes it much easier to use HashiCorp Vault for securely storing and managing your sensitive information, without needing to remember all the complex commands and procedures.
Code Analysis of BTCwallet.ps1
The script generally follows sound design principles with good organization, comments, and documentation. It demonstrates thoughtful error checking and user interaction. The identified opportunities for enhancement would primarily improve security, maintainability, and robustness rather than addressing fundamental flaws. The script author has clearly put significant effort into creating a comprehensive tool with good documentation and practical functionality.
BTCwallet.ps1 Explanation
The BTCwallet.ps1 script is a PowerShell tool designed to help Bitcoin users manage different wallet applications on a Linux system. It provides a convenient way to start, stop, and check the status of Bitcoin wallets while adding security features.
Purpose
The main purpose of this script is to securely manage Bitcoin wallets, particularly focusing on "cold storage" solutions. Cold storage means keeping your Bitcoin wallet data in an encrypted container that's only mounted when needed, which is more secure than keeping it always accessible ("hot storage").
Inputs
The script takes one main input parameter:
$action: This can be "start", "stop", or "check" (default), telling the script what operation to perform on your Bitcoin wallet.
Outputs
The script doesn't return data but produces several visible outputs:
- Status messages showing whether wallets are running or stopped
- Prompts for user input when decisions are needed
- Confirmation messages when actions are completed
How It Works
-
When you run the script, it first loads a configuration file (BTCwalletCfg.xml) that contains information about which wallets you have installed.
-
Based on the
$actionparameter, it performs one of three main functions:- Check: Shows if your wallet application is currently running
- Start: Launches your wallet application, with options for hot or cold storage
- Stop: Closes your wallet application and securely dismounts any encrypted containers
- For security, the script can use HashiCorp Vault (a secure password manager) to store sensitive information like passwords for encrypted containers.
-
The script also verifies its own integrity by checking its file hash against a previously stored value, alerting you if the script has been modified.
Important Logic Flows
Starting a Wallet
When starting a wallet, the script:
- Asks which wallet you want to use (Sparrow, GreenWallet, or Wasabi)
- Checks if HashiCorp Vault is running and starts it if needed
- Verifies the script's integrity by comparing file hashes
- Asks if you want to use hot or cold storage
- For cold storage, it:
- Retrieves the encrypted container's location and password
- Mounts the encrypted container using VeraCrypt
- Starts the wallet application pointing to the mounted container
- For hot storage, it simply starts the wallet application with default settings
Stopping a Wallet
When stopping a wallet, the script:
- Checks if the wallet is still running and asks you to close it first if needed
- For cold storage wallets, it moves any wallet files back to the encrypted container
- Dismounts the encrypted container
- Optionally stops the HashiCorp Vault service
The script handles different wallet applications (Sparrow, GreenWallet, and Wasabi) slightly differently based on how each one stores its data and what command-line options they support.
In summary, BTCwallet.ps1 provides a secure way to manage Bitcoin wallets by combining wallet applications with encrypted storage and password management, all controlled through simple commands.
- An
-
 @ cae03c48:2a7d6671
2025-05-23 13:01:01
@ cae03c48:2a7d6671
2025-05-23 13:01:01Bitcoin Magazine

Michael Saylor’s Strategy (MSTR) Opens $2.1B ATM Program for Strife Preferred StockStrategy has launched a $2.1 billion At-The-Market (ATM) equity program for its Strife (STRF) preferred stock, marking another step in the firm’s long-term strategy to build a Bitcoin-backed financial architecture.
The announcement was made by CEO and President Phong Lee during an investor update alongside Executive Chairman Michael Saylor. According to Lee, strong year-to-date results from the firm’s Bitcoin-linked securities Strike (STRK) and Strife (STRF) gave Strategy the confidence to expand its fundraising strategy.
BREAKING:
 Strategy to sell up to $2.1 billion of 10% preferred stock.pic.twitter.com/xufD8uv64v
Strategy to sell up to $2.1 billion of 10% preferred stock.pic.twitter.com/xufD8uv64v— Bitcoin Magazine (@BitcoinMagazine) May 22, 2025
“We’re currently at 16.3% BTC yield for the year, against a 25% target,” Lee said. “BTC dollar gain is $7.7 billion so far, on track toward our $15 billion target.”
Both instruments have outperformed expectations since launch. Strike is up 24% from its initial price of $80 to nearly $100. Strife, which was priced at $85 just two months ago, now trades around $98.80, a 16% increase. By comparison, similarly structured preferreds in the market have declined by 3–5% over the same period.

In the last 30 days alone, Strike rose 17% and Strife 12%, bringing both close to par value. Lee emphasized the liquidity profile of these instruments, citing average daily trading volumes of $31 million for Strike and $23 million for Strife. “That’s 60x what we typically see in comparable preferreds,” he noted.
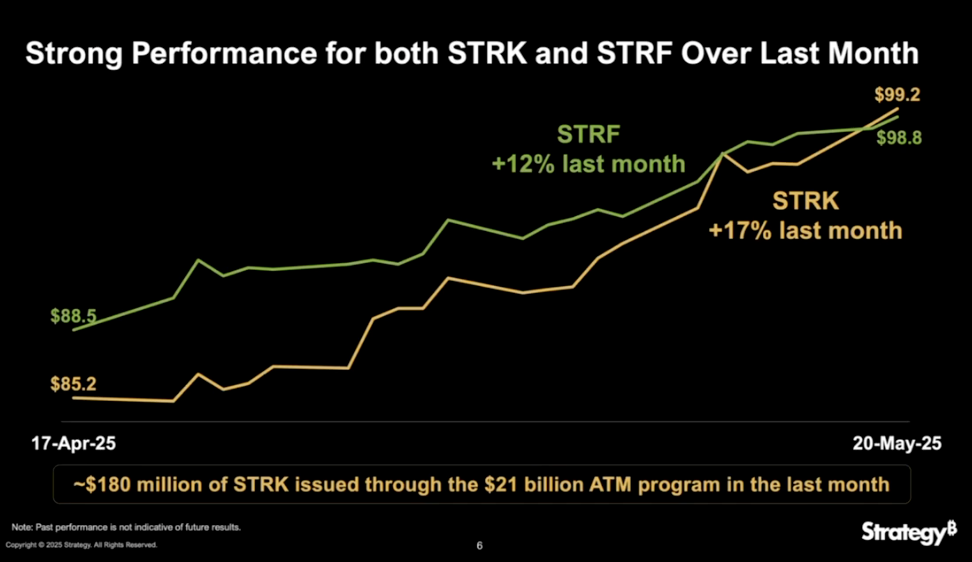
The company previously issued $212 million through Strike’s ATM, with no adverse pricing pressure. Based on the trading volume and investor demand, Lee said the company believes the $2.1 billion Strife ATM can be executed in a similar fashion.
Strife is a perpetual preferred stock with a 10% coupon and sits at the top of Strategy’s capital stack. Saylor described it as “the crown jewel” of the company’s preferred offerings. “We’re going to be ten times as careful with Strife,” he said. “Our goal is for it to be seen as investment-grade fixed income — a high-quality instrument with robust protections.”
Strike, by contrast, is positioned for what Saylor called “Bitcoin-curious” investors. It carries an 8% coupon and includes upside through Bitcoin conversion. “Think of it like a Bitcoin fellowship with a stipend,” Saylor said.
Strategy now operates three ATM programs: $21 billion each for MSTR equity and Strike, and $2.1 billion for Strife. These are rebalanced daily, with issuance adjusted based on market conditions, volatility, and investor demand. According to Saylor, this dynamic structure allows the company to optimize Bitcoin acquisition and capital deployment across changing market environments.
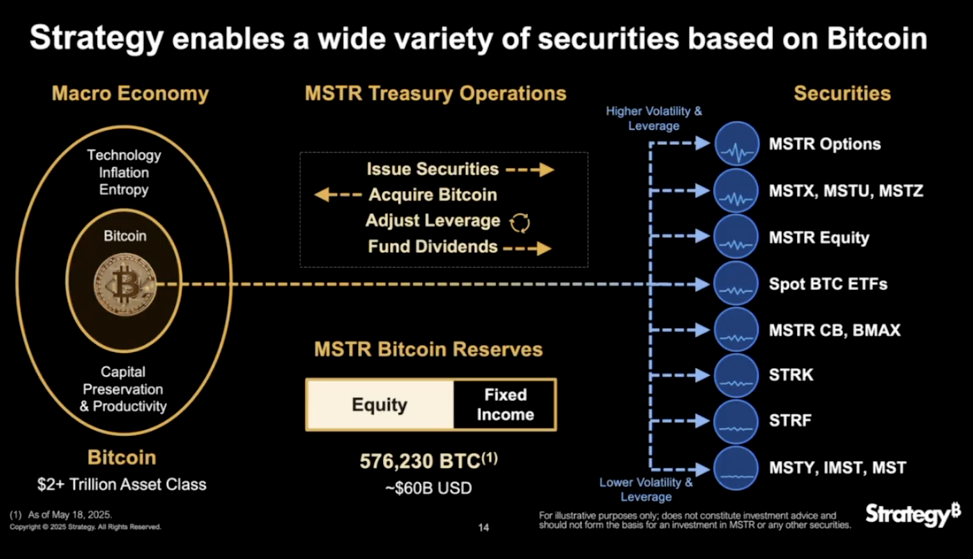
Behind this strategy sits Strategy’s Bitcoin treasury, now totaling 576,230 BTC — roughly $60 billion in value. “That permanent capital is the foundation for everything we’re building,” Saylor said.
While spot Bitcoin ETFs cater to investors looking for direct price exposure, Strategy continues to offer a more nuanced set of instruments — each targeting different levels of risk, return, and compliance. The Strife ATM is the latest move in that broader strategy.
This post Michael Saylor’s Strategy (MSTR) Opens $2.1B ATM Program for Strife Preferred Stock first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ cae03c48:2a7d6671
2025-05-23 13:01:00
@ cae03c48:2a7d6671
2025-05-23 13:01:00Bitcoin Magazine

H100 Group Became The First Publicly Listed Bitcoin Treasury Company In SwedenH100 Group AB has announced it has become Sweden’s first publicly listed health technology company to adopt Bitcoin as a treasury reserve asset, announcing the purchase of 4.39 BTC for 5 million NOK (approximately $475,000) as part of its long-term Bitcoin Treasury Strategy.
The Stockholm-based company, which provides AI-powered automation and digital solutions for healthcare providers, joins a growing roster of public companies adding Bitcoin to their balance sheets in 2025. The purchase was executed at an average price of 1,138,737 NOK per Bitcoin (roughly $108,200).
JUST IN:
 H100 Group buys 4.39 BTC and becomes Sweden's first publicly listed #Bitcoin treasury company. pic.twitter.com/pNXe9XT2a7
H100 Group buys 4.39 BTC and becomes Sweden's first publicly listed #Bitcoin treasury company. pic.twitter.com/pNXe9XT2a7— Bitcoin Magazine (@BitcoinMagazine) May 22, 2025
“This addition to H100’s Bitcoin Treasury Strategy follows an increasing number of tech-oriented growth companies holding Bitcoin on their balance sheet,” said CEO Sander Andersen. “And I believe the values of individual sovereignty highly present in the Bitcoin community aligns well with, and will appeal to, the customers and communities we are building the H100 platform for.”
The move comes amid a surge in corporate Bitcoin adoption, with many public companies announcing Bitcoin treasury programs in the first five months of 2025. Notable recent entrants include Twenty One Capital, Strive and several others.
H100 Group emphasized that the Bitcoin purchase does not affect its core operations in the health and longevity industry. The company views the investment as a strategic deployment of excess liquidity to strengthen its financial position while aligning with its values of individual sovereignty.
The announcement reflects a broader shift in corporate treasury management, as companies seek to diversify their holdings beyond traditional cash reserves.
At press time, Bitcoin trades at $111,108, up 1.28% over the past 24 hours, as institutional adoption continues to drive market momentum. H100 Group’s shares closed up 1.37% at 0.89 SEK on the NGM Nordic SME exchange following the announcement.
This post H100 Group Became The First Publicly Listed Bitcoin Treasury Company In Sweden first appeared on Bitcoin Magazine and is written by Vivek Sen.
-
 @ 7e6f9018:a6bbbce5
2025-05-22 16:33:07
@ 7e6f9018:a6bbbce5
2025-05-22 16:33:07Per les xarxes socials es parla amb efusivitat de que Bitcoin arribarà a valer milions de dòlars. El mateix Hal Finney allà pel 2009, va estimar el potencial, en un cas extrem, de 10 milions $:
\> As an amusing thought experiment, imagine that Bitcoin is successful and becomes the dominant payment system in use throughout the world. Then the total value of the currency should be equal to the total value of all the wealth in the world. Current estimates of total worldwide household wealth that I have found range from $100 trillion to $300 trillion. Withn 20 million coins, that gives each coin a value of about $10 million. <https://satoshi.nakamotoinstitute.org/emails/bitcoin-list/threads/4/>
No estic d'acord amb els càlculs del bo d'en Hal, ja que no consider que la valoració d'una moneda funcioni així. En qualsevol cas, el 2009 la capitalització de la riquesa mundial era de 300 bilions $, avui és de 660 bilions $, és a dir ha anat pujant un 5,3% de manera anual,
$$(660/300)^{1/15} = 1.053$$La primera apreciació amb aquest augment anual del 5% és que si algú llegeix aquest article i té diners que no necessita aturats al banc (estalvis), ara és bon moment per començar a moure'ls, encara sigui amb moviments defensius (títols de deute governamental o la propietat del primer habitatge). La desagregació per actius dels 660 bilions és:
-
Immobiliari residencial = 260 bilions $
-
Títols de deute = 125 bilions $
-
Accions = 110 bilions
-
Diners fiat = 78 bilions $
-
Terres agrícoles = 35 bilions $
-
Immobiliari comercial = 32 bilions $
-
Or = 18 bilions $
-
Bitcoin = 2 bilions $
La riquesa mundial és major que 660 bilions, però aquests 8 actius crec que són els principals, ja que s'aprecien a dia d'avui. El PIB global anual és de 84 bilions $, que no són bromes, però aquest actius creats (cotxes, ordinadors, roba, aliments...), perden valor una vegada produïts, aproximant-se a 0 passades unes dècades.
Partint d'aquest nombres com a vàlids, la meva posició base respecte de Bitcoin, ja des de fa un parell d'anys, és que te capacitat per posar-se al nivell de capitalització de l'or, perquè conceptualment s'emulen bé, i perquè tot i que Bitcoin no té un valor tangible industrial com pot tenir l'or, sí que te un valor intangible tecnològic, que és pales en tot l'ecosistema que s'ha creat al seu voltant:
-
Creació de tecnologies de pagament instantani: la Lightning Network, Cashu i la Liquid Network.
-
Producció d'aplicacions amb l'íntegrament de pagaments instantanis. Especialment destacar el protocol de Nostr (Primal, Amethyst, Damus, Yakihonne, 0xChat...)
-
Industria energètica: permet estabilitzar xarxes elèctriques i emprar energia malbaratada (flaring gas), amb la generació de demanda de hardware i software dedicat.
-
Educació financera i defensa de drets humans. És una eina de defensa contra governs i estats repressius. La Human Rights Foundation fa una feina bastant destacada d'educació.
Ara posem el potencial en nombres:
-
Si iguala l'empresa amb major capitalització, que és Apple, arribaria a uns 160 mil dòlars per bitcoin.
-
Si iguala el nivell de l'or, arribaria a uns 800 mil dòlars per bitcoin.
-
Si iguala el nivell del diner fiat líquid, arribaria a un 3.7 milions de dòlars per bitcoin.
Crec que igualar la capitalització d'Apple és probable en els pròxims 5 - 10 anys. També igualar el nivell de l'or en els pròxims 20 anys em sembla una fita possible. Ara bé, qualsevol fita per sota d'aquesta capitalització ha d'implicar tota una serie de successos al món que no sóc capaç d'imaginar. Que no vol dir que no pugui passar.
-
-
 @ da8b7de1:c0164aee
2025-05-22 16:19:52
@ da8b7de1:c0164aee
2025-05-22 16:19:52Technológiai és fejlesztési hírek
- Észtország SMR-tervei:
Észtország hivatalosan elindította a nemzeti tervezési folyamatot és a környezeti hatásvizsgálatot egy 600 MW-os kis moduláris reaktor (SMR) atomerőmű létesítésére, GE Hitachi BWRX-300 technológiával. A projektet a Fermi Energia vezeti, a lakosság körében mérsékelt támogatottság mellett. Az építési engedélykérelem benyújtását 2029-re tervezik, a cél az ország energiabiztonságának és klímacéljainak erősítése.
- Olkiluoto-1 csökkentett teljesítménnyel üzemel:
Finnországban az Olkiluoto-2 egységben a generátor rotorjának cseréje miatt a termelés májusban újraindul, de a teljesítményt 735 MW-ra korlátozzák (a teljes kapacitás 890 MW). A csökkentett teljesítmény 2026-ig marad érvényben. Az Olkiluoto-1 egység normálisan működik, az Olkiluoto-3 pedig éves karbantartáson van.
Ipari és pénzügyi fejlemények
- Kanada–Argentína nehézvíz-együttműködés:
A kanadai Candu Energy (AtkinsRéalis) és az argentin Nemzeti Atomenergia Bizottság (CNEA) memorandumot írt alá a nehézvíz-termelés fellendítéséről. Ez magában foglalja az argentin PIAP nehézvízgyár újraindítását és potenciálisan új üzemek építését Kanadában. A fejlesztés támogatja a meglévő és tervezett CANDU reaktorok működését világszerte, és illeszkedik a COP28 utáni globális nukleáris bővüléshez.
- USA: nukleáris adókedvezményekért folyó lobbizás:
Az amerikai nukleáris ipar intenzív lobbitevékenységet folytat, hogy megőrizze a Biden-adminisztráció által bevezetett, az Inflációcsökkentő Törvény (IRA) szerinti nukleáris adókedvezményeket. Az új, republikánus többségű költségvetési törvényjavaslat jelentősen lerövidítené a tiszta energia (szél, nap, akkumulátor) támogatásokat, de a nukleáris ipar számára bizonyos kedvezmények megmaradnának, bár a 45U nukleáris adókedvezmény is három évvel korábban, 2031-ben lejárhat.
- Háztartási és ipari érdekek:
Az amerikai ház költségvetési törvényjavaslata megszüntetné a legtöbb tiszta energiához kapcsolódó adókedvezményt, kivéve néhány nukleáris projektet, és szigorítaná a kínai kapcsolatokkal rendelkező projektek támogatását. Ez várhatóan visszaveti a megújuló energiaipar beruházásait, miközben a nukleáris szektor relatív pozíciója javulhat.
Politikai és társadalmi fejlemények
- Tajvan: népszavazás a nukleáris energia sorsáról:
Tajvan parlamentje megszavazta, hogy népszavazást tartsanak a Maanshan atomerőmű újraindításáról, miután az ország utolsó működő reaktorát is leállították. A referendum nem azonnali újraindításról szól, hanem arról, hogy a lakosság döntsön a meghosszabbításról, ha a hatóságok biztonságosnak találják az üzemet.
- Pennsylvania kormányzója a nukleáris energia mellett:
Josh Shapiro, Pennsylvania kormányzója, a „Lightning Plan” keretében hangsúlyozta, hogy az állam energiabiztonsága és gazdasági fejlődése érdekében kulcsszerepet szán a nukleáris energiának, valamint más megbízható energiaforrásoknak. A terv célja a munkahelyteremtés, a fogyasztói költségek csökkentése és az engedélyezési folyamatok gyorsítása.
- TMI névváltás:
Az amerikai Nukleáris Szabályozó Hatóság (NRC) jóváhagyta a Three Mile Island (TMI) atomerőmű nevének megváltoztatását Christopher M. Crane-re, az Exelon volt vezérigazgatójának emlékére. A létesítmény a jövőben a Microsoft AI műveleteit is ellátja majd árammal, és 2028-tól 835 MW szén-dioxid-mentes áramot termelhet.
Nemzetközi szakmai események
- NEA konferencia Londonban:
Az OECD NEA 2025. június 18–19-én Londonban rendezi meg az „Excellence in Nuclear Construction” nemzetközi konferenciát. A rendezvény célja, hogy a nukleáris ipar szereplői megosszák tapasztalataikat a nukleáris beruházások gyorsabb, kiszámíthatóbb és költséghatékonyabb megvalósítása érdekében, különös tekintettel a mérnöki, beszerzési és kivitelezési (EPC) kihívásokra.
Hivatkozások
- https://www.nucnet.org
- https://www.world-nuclear-news.org
- https://www.neimagazine.com
- https://www.oecd-nea.org
- https://www.iaea.org
- https://www.reuters.com/business/energy
- https://www.utilitydive.com
- https://www.atkinsrealis.com
- https://www.candu.com
-
 @ cae03c48:2a7d6671
2025-05-23 13:00:59
@ cae03c48:2a7d6671
2025-05-23 13:00:59Bitcoin Magazine

The Freedom Issue: Letter From the EditorBitcoin is freedom money, a censorship-resistant form of digital cash allowing anyone with an internet connection to send money to anyone else, regardless of nationality, borders, or other arbitrary restrictions.
I personally first heard about Bitcoin in early 2013, through friends who were buying… stuff from Silk Road, the darknet marketplace helmed by the mysterious Dread Pirate Roberts. Although Silk Road was controversial (the “stuff” most people bought and sold was, of course, illegal drugs), it represented a radical example of the form of freedom that Bitcoin provides.
Later in 2013, Silk Road was shut down by the FBI, and Ross Ulbricht was revealed as the market’s founder and the true identity behind the Dread Pirate Roberts pseudonym — although he claims several people operated the account. Ulbricht was sentenced to two life sentences plus forty years in prison without the possibility of parole.
In my view — and that of many Bitcoiners — it was excessive. Even if you believe Ulbricht was guilty of everything he was convicted of (all nonviolent crimes), he was made an example of, and didn’t actually deserve to be locked up for the rest of his days.
Fortunately, Ulbricht was granted a full and unconditional pardon from President Trump in January of this year. The founder of Silk Road, in a very literal sense, has regained his freedom.
This edition of Bitcoin Magazine celebrates and highlights the freedom aspect of Bitcoin with a range of articles and artwork focusing on the people and projects that use bitcoin to advance liberty, and those who make this possible… with a special focus on Ulbricht and Silk Road.
For other stories about bitcoin as freedom money, flip the magazine around!
Welcome to The Freedom Issue.
Aaron van Wirdum
Don’t miss your chance to own The Freedom Issue—featuring never-before-seen letters from Ross Ulbricht and his mother, Lyn. Limited run. Only available while supplies last.
This piece is the Letter from the Editor featured in the latest print edition of Bitcoin Magazine, The Freedom Issue. We’re sharing it here as an early look at the ideas explored throughout the full issue.
This post The Freedom Issue: Letter From the Editor first appeared on Bitcoin Magazine and is written by Aaron Van Wirdum.
-
 @ cae03c48:2a7d6671
2025-05-23 13:00:58
@ cae03c48:2a7d6671
2025-05-23 13:00:58Bitcoin Magazine
Bitcoin Pizza Day: 15 Years Since 10,000 BTC Bought Two Pizzas and Changed EverythingOn May 22, 2010, Bitcoin became more than just an idea—it became real money. Laszlo Hanyecz, a developer and early contributor to Bitcoin’s codebase, posted a casual offer: “I’ll pay 10,000 bitcoins for a couple of pizzas.” Five days later, someone took him up on it. Two Papa John’s pizzas were delivered. A screenshot was posted. Bitcoin had entered the real world.
15 years ago, Laszlo Hanyecz spent 10,000 #bitcoin worth $30 on two Papa John's pizzas.
Today, 10,000 $BTC is worth over $1,100,000,000.
What a legend!
 pic.twitter.com/EbxQAsixhZ
pic.twitter.com/EbxQAsixhZ— Bitcoin Magazine (@BitcoinMagazine) May 22, 2025
That 10,000 Bitcoin, worth about $41 at the time, is now valued at over $1.1 billion. And with Bitcoin hitting a new all-time high of $111,999 on the 15th anniversary of the transaction, the story of the “Bitcoin Pizza” carries more weight than ever.
15 years ago, someone paid 10,000 #Bitcoin for 2 pizzas. That’s worth over $1,000,000,000 today!

It wasn’t just about the pizza. This was the moment Bitcoin proved itself as a functioning currency. Until then, it had lived mostly in theory and code—talked about by cryptographers and mined by hobbyists. Hanyecz’s post, and the trade that followed, transformed the idea into action. “This transaction made Bitcoin real in my eyes,” he said in a 2019 interview. “It wasn’t worth much at the time. I wouldn’t have spent $100 million on pizza, right? But if I hadn’t done that, maybe Bitcoin wouldn’t have become so popular.”
Over the summer of 2010, Hanyecz continued using Bitcoin to buy pizzas, eventually spending more than 79,000 BTC—now worth nearly $8.7 billion. While some have joked at his expense, the truth is this: without those early real-world transactions, Bitcoin might never have proven its use case. Hanyecz helped move Bitcoin from the fringe into functionality.
That legacy still shapes us today. Bitcoin Pizza Day has become a cultural milestone in the crypto world, with meetups, pizza parties, and educational events held globally each May 22. The day serves as a reminder of how far the technology has come—and the importance of everyday actions and the impact they have.
Smiles, joy, and shared moments, this is what today looked like.#Bitcoin Pizza Day at His Grace School was more than a visit. It was connection, care, and community. A heartfelt thank you to everyone who donated and supported #BitcoinGhana #BitcoinPizzaDay #BTC #Bitfiasi pic.twitter.com/xRMv1rpife
— Bitfiasi Initiative (@bitfiasi) May 22, 2025
Just this week, fast food chain Steak ‘n Shake began accepting Bitcoin via the Lightning Network, signaling a growing wave of mainstream adoption. What once felt experimental is now becoming part of everyday commerce.
Bitcoin Pizza Day is about recognition. One simple transaction proved that Bitcoin could work—and 15 years later, the world is still building on that first bite.
This post Bitcoin Pizza Day: 15 Years Since 10,000 BTC Bought Two Pizzas and Changed Everything first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ 7e6f9018:a6bbbce5
2025-05-22 15:44:12
@ 7e6f9018:a6bbbce5
2025-05-22 15:44:12Over the last decade, birth rates in Spain have dropped by 30%, from 486,000 births in 2010 to 339,000 in 2020, a decline only comparable to that seen in Japan and the Four Asian Tigers.
The main cause seems to stem from two major factors: (1) the widespread use of contraceptive methods, which allow for pregnancy control without reducing sexual activity, and (2) women's entry into the labor market, leading to a significant shift away from traditional maternal roles.
In this regard, there is a phenomenon of demographic inertia that I believe could become significant. When a society ages and the population pyramid inverts, the burden this places on the non-dependent population could further contribute to a deeper decline in birth rates.

The more resources (time and money) non-dependent individuals have to dedicate to the elderly (dependents), the less they can allocate to producing new births (also dependents):
- An only child who has to care for both parents will bear a burden of 2 (2 ÷ 1).
- Three siblings who share the responsibility of caring for their parents will bear a burden of 0.6 (2 ÷ 3).
This burden on only children could, in many cases, be significant enough to prevent them from having children of their own.
In Spain, the generation of only children reached reproductive age in 2019(*), this means that right now the majority of people in reproductive age in Spain are only child (or getting very close to it).
If this assumption is correct, and aging feeds on itself, then, given that Spain has one of the worst demographic imbalances in the world, this phenomenon is likely to manifest through worsening birth rates. Spain’s current birth rate of 1.1 may not yet have reached its lowest point.
(*)Birth rate table and the year in which each generation reaches 32 years of age, Spain.
| Year of birth | Birth rate | Year in which the generation turns 32 | | ------------------ | -------------- | ----------------------------------------- | | 1971 | 2.88 | 2003 | | 1972 | 2.85 | 2004 | | 1973 | 2.82 | 2005 | | 1974 | 2.81 | 2006 | | 1975 | 2.77 | 2007 | | 1976 | 2.77 | 2008 | | 1977 | 2.65 | 2009 | | 1978 | 2.54 | 2010 | | 1979 | 2.37 | 2011 | | 1980 | 2.21 | 2012 | | 1981 | 2.04 | 2013 | | 1982 | 1.94 | 2014 | | 1983 | 1.80 | 2015 | | 1984 | 1.72 | 2016 | | 1985 | 1.64 | 2017 | | 1986 | 1.55 | 2018 | | 1987 | 1.49 | 2019 | | 1988 | 1.45 | 2020 | | 1989 | 1.40 | 2021 | | 1990 | 1.36 | 2022 | | 1991 | 1.33 | 2023 | | 1992 | 1.31 | 2024 | | 1993 | 1.26 | 2025 | | 1994 | 1.19 | 2026 | | 1995 | 1.16 | 2027 | | 1996 | 1.14 | 2028 | | 1997 | 1.15 | 2029 | | 1998 | 1.13 | 2030 | | 1999 | 1.16 | 2031 | | 2000 | 1.21 | 2032 | | 2001 | 1.24 | 2033 | | 2002 | 1.25 | 2034 | | 2003 | 1.30 | 2035 | | 2004 | 1.32 | 2036 | | 2005 | 1.33 | 2037 | | 2006 | 1.36 | 2038 | | 2007 | 1.38 | 2039 | | 2008 | 1.44 | 2040 | | 2009 | 1.38 | 2041 | | 2010 | 1.37 | 2042 | | 2011 | 1.34 | 2043 | | 2012 | 1.32 | 2044 | | 2013 | 1.27 | 2045 | | 2014 | 1.32 | 2046 | | 2015 | 1.33 | 2047 | | 2016 | 1.34 | 2048 | | 2017 | 1.31 | 2049 | | 2018 | 1.26 | 2050 | | 2019 | 1.24 | 2051 | | 2020 | 1.19 | 2052 |
-
 @ 4fa5d1c4:fd6c6e41
2025-05-22 15:30:43
@ 4fa5d1c4:fd6c6e41
2025-05-22 15:30:43🧠 Entwickelt von OECD & EU-Kommission – jetzt zur Rückmeldung freigegeben:\ 👉 https://ailiteracyframework.org/
Das Framework beschreibt vier zentrale Domänen der KI-Kompetenz – jede mit einem klaren Profil aus Wissen, Fertigkeiten und Haltungen. Diese lassen sich hervorragend mit den vier Kompetenzbereichen verbinden:
🔹 Engaging with AI ↔ 🟢 Verstehen
Lernende erkennen KI in ihrem Alltag, verstehen ihre technischen Grundlagen (📘 Knowledge) und entwickeln die Fähigkeit, Ausgaben kritisch zu analysieren (🛠️ Skills), begleitet von einer neugierigen und verantwortungsbewussten Einstellung (🧭 Attitudes).
🔹 Creating with AI ↔ 🔵 Anwenden
Durch den kreativen Einsatz generativer KI entstehen neue Lernprodukte. Benötigt werden technisches Verständnis (📘 z. B. zu Trainingsdaten), Anwendungskompetenz (🛠️ z. B. Promptgestaltung), sowie eine innovationsorientierte Haltung (🧭 Ownership, Urheberrecht, Attribution).
🔹 Managing AI ↔ 🟠 Reflektieren
Hier geht es um bewusste Entscheidungen: Wann ist KI sinnvoll? Wie wirken sich ihre Vorschläge auf mein Denken aus? Das verlangt (📘) Orientierungswissen, (🛠️) strategisches Problemlösen und (🧭) eine ethisch begründbare Reflexion.
🔹 Designing AI ↔ 🟣 Gestalten
Lernende analysieren und entwerfen KI-Systeme: Welche Daten nutze ich? Wer profitiert? Mit welchen Folgen? Die Verbindung aus (📘) systemischem Wissen, (🛠️) Gestaltungskompetenz und (🧭) ethischer Haltung eröffnet Bildungsräume im digitalen Wandel.
📬 Rückmeldungen zum Entwurf sind willkommen – eure Expertise aus der Praxis zählt!
👉 [https://teachai.org/ailiteracy/review](https://teachai.org/ailiteracy/review)
-
 @ cae03c48:2a7d6671
2025-05-23 13:00:57
@ cae03c48:2a7d6671
2025-05-23 13:00:57Bitcoin Magazine

The Citadel (v. Nardo): From Meme to Monument
My latest painting, The Citadel (v. Nardo), did not begin simply on canvas. It began as a whisper – an image passed digitally between anonymous hands, reposted, remixed, archived, and mythologized across the internet. Like many of my works, this piece builds from historical fragments and symbols, grounded in the belief that memes are not fleeting – they are foundational. They don’t just reflect culture, rather, they write it.
Last year in 2024, I presented a solo show in Abu Dhabi centered around the fact that Subway – the sandwich chain – was one of the first fast food restaurants to accept Bitcoin. That small historical detail became the seed of a larger conceptual inquiry: what does it mean to “consume” in an age of hyper-speed information? The works explored the overlap between fast food, memes, and digital attention. The exhibition was tight, precise, and deeply memetic in its structure.
The Citadel came from a similar place.
In 2013, a now-legendary Reddit post titled “I am a time-traveler from the future, here to beg you to stop what you are doing” appeared online. The author – claiming to be from 2025 – warned of a future shaped by Bitcoin, but not in the way many had hoped. It wasn’t a utopia. It was a stratified society where those who adopted early became untouchably rich, and everyone else was left behind. Whether satire, fiction, or genuine warning, the post struck a nerve. It spread quickly. It became part of the cultural and memetic architecture of Bitcoin.
Years later, another anonymous user gave that warning a visual form. The Citadel v.1, likely created on 4chan, featured a massive tower cobbled together from borrowed imagery – most notably a background ripped from Alexander Mikhalchyk’s oil painting Tower of Babel. Red – overlaid with iconic internet figures like Pepe, Wojak, and the Bogdanoff twins. It was chaotic, funny, ominous. And it caught fire. Versions spread across forums. Variants emerged for Monero, Ethereum, and other Bitcoin-based class hierarchies. A whole mythology took shape around it.


I couldn’t stop thinking about that image. The symbolism. The verticality. The warning. It wasn’t just a meme – it was a map. A visual schema of power and belief, told in the language of the internet. And yet, it had never been physically painted. Never given the weight or permanence it deserved. That’s when I decided to create what I believe is the first fully hand-painted oil version of the Bitcoin Citadel meme.
The Citadel (v. Nardo) is 7 feet wide, 5 feet tall, and entirely rendered in oil by hand over six months. The tower in my painting is original – constructed from references to Bruegel’s depictions of Babel. The superimposed depictions of Pepe, the monk, the nobleman, even Jesus, are deliberate nods to the v.1 version, reimagined and integrated with painterly care. Nothing here is copy-pasted. Every inch is built to feel mythic, monumental, and true to the weight of the meme itself.
Like all my work, it’s meant to evoke grandeur, drama, and symbolic density. It’s meant to feel like a relic from a future past – something dug up from the ruins of digital civilization. My late professor once told me that the best art is both folkloric and provocative. That line never left me.
And that’s essentially what internet memes are. They are modern folklore. They encode belief, identity, warning, and aspiration in compressed symbols. They may start as jokes – but jokes have always been a delivery system for deeper truth. Memes don’t just survive online; they shape what we expect from reality.
The Citadel (v. Nardo) will be sold at auction via Scarce.City and debut at the Bitcoin Conference in Las Vegas – the largest gathering of Bitcoiners in the world. It’s not just a painting. It’s a response. A reckoning. A reminder.Because in the end, as I always say: you become what you meme.
This is a guest post by X-Nardo Opinions expressed are entirely their own and do not necessarily reflect those of BTC, Inc. or Bitcoin Magazine_._
This post The Citadel (v. Nardo): From Meme to Monument first appeared on Bitcoin Magazine and is written by X-Nardo.
-
 @ 63d59db8:be170f6f
2025-05-23 12:53:00
@ 63d59db8:be170f6f
2025-05-23 12:53:00In a world overwhelmed by contradictions—climate change, inequality, political instability, and social disconnection—absurdity becomes an unavoidable lens through which to view the human condition. Inspired by Albert Camus' philosophy, this project explores the tension between life’s inherent meaninglessness and our persistent search for purpose.\ \ The individuals in these images embody a quiet defiance, navigating chaos with a sense of irony and authenticity. Through the act of revolt—against despair, against resignation—they find agency and resilience. These photographs invite reflection, not on solutions, but on our capacity to live meaningfully within absurdity.
Visit Katerina's website here.
Submit your work to the NOICE Visual Expression Awards for a chance to win a few thousand extra sats:
-
 @ 975e4ad5:8d4847ce
2025-05-22 14:30:53
@ 975e4ad5:8d4847ce
2025-05-22 14:30:53The Risks of Offline Storage
Keeping your seed phrase offline – on paper, in a safe, or on a USB drive – seems secure, but it comes with significant risks:
-
Fire or Flood: A disaster could destroy your home, along with the paper or device storing your seed phrase.
-
Theft: Someone could find your seed phrase in your safe or a hidden spot at home.
-
Natural Disasters or War: If you’re forced to leave your home, you might lose access to your seed phrase, effectively locking you out of your assets.
-
Human Error: You could accidentally lose, damage, or misplace the paper or device holding your seed phrase.
These vulnerabilities make offline storage less reliable, especially if you don’t have backups or can’t access them in an emergency.
The Benefits of Online Storage
When done right, online storage addresses these issues. The primary advantage is accessibility: you can retrieve your seed phrase from anywhere in the world as long as you have an internet connection and the necessary credentials. This is invaluable if you’re away from home or in a crisis.
The key to making online storage safe? Encryption.
How to Store Your Seed Phrase Online Securely
-
Choose a Secure Platform\ Upload your encrypted seed phrase to a reputable cloud storage service like Google Drive, Dropbox, or Proton Drive, which offers built-in encryption. Ensure you use a strong password and enable two-factor authentication (2FA) for your account.
-
Encrypt Your Seed Phrase\ Before uploading, encrypt your seed phrase using a tool with strong encryption, such as AES-256. Here are some easy options:
-
VeraCrypt: A free tool that lets you create an encrypted file or container. Save your seed phrase in a text file, add it to an encrypted container, and set a password only you know.
-
GPG (GnuPG): This tool allows you to encrypt text files using public and private keys. Generate a key pair and store the private key securely (e.g., on an offline USB drive).
-
7-Zip: A popular compression tool that supports AES-256 encryption. Create an encrypted archive with your seed phrase and set a strong password.
-
Keep the Decryption Key in Your Head\ The password or decryption key should be something only you know. Avoid writing it down to prevent unauthorized access.
-
Disguise the File\ Even if someone sees your encrypted file, they shouldn’t suspect what it contains. Name the file something generic, like “family_recipes.txt,” instead of “seed_phrase.txt.”
Why Encryption Matters
Encryption ensures that even if someone gains access to your file, they can’t read your seed phrase without the decryption key. AES-256, for example, is an industry-standard encryption method considered virtually unbreakable with a strong password. This means that even if a hacker accesses your cloud storage, they can’t use your seed phrase.
Practical Tips for Maximum Security
-
Split Your Seed Phrase: For added protection, divide your seed phrase into multiple parts and store them in separate encrypted files on different platforms.
-
Test Your Access: Periodically check that you can log into your cloud storage and decrypt your file to avoid surprises.
-
Use a Strong Password: Choose a password longer than 12 characters, combining letters, numbers, and special characters.
-
Create Backups: Store multiple encrypted copies on different platforms for extra redundancy.
Conclusion
Storing your seed phrase online isn’t reckless if you do it right. With proper encryption and a secure platform, you can combine the convenience of global access with a high level of protection. Offline methods have their risks, but secure online storage ensures your assets are safe and accessible, no matter where you are.
-
-
 @ 2b468756:7930dd9c
2025-05-23 12:41:01
@ 2b468756:7930dd9c
2025-05-23 12:41:01Agorisme is libertarisme in de praktijk: op legale wijze maximale economische en persoonlijke vrijheid. Samen ontdekken en delen we wat er allemaal mogelijk is. We doen dit door: - organiseren jaarlijks agorismefestival - organiseren meerdere themadagen / excursies per jaar - bundelen praktische kennis op Agorisme Wiki - online uitwisselen via (thema)appgroepen
Op deze site worden activiteiten aangekondigd en kun je je opgeven.
Binnenkort: - cursussen metselen, stucen en vloeren - reis naar libertarisch dorp Walden Woods en Liberstad in Noorwegen - introductie Krav Maga zelfverdediging
We zijn gelieerd aan de libertarische partij.
Graag tot ziens!
-
 @ 90152b7f:04e57401
2025-05-22 14:27:51
@ 90152b7f:04e57401
2025-05-22 14:27:51Wikileaks - C O N F I D E N T I A L SECTION 01 OF 02 JERUSALEM 002018 SIPDIS SIPDIS NEA FOR FRONT OFFICE; NEA/IPA FOR GOLDBERGER/SHAMPAINE/BELGRADE; NSC FOR ABRAMS/WATERS; TREASURY FOR SZUBIN/GRANT/HARRIS/NUGENT/HIRSON E.O. 12958: DECL: 07/17/17 TAGS: ECON, EFIN, KFTN, KWBG, IS
2007 September 26
SUBJECT: ISRAELI BANK CUTOFF PORTENDS GAZA BANK CLOSURES AND MORE PRIVATE SECTOR DIFFICULTIES Classified By: Consul General Jake Walles,
Reasons 1.4 (b) and (d). 1. 1. (SBU) Summary. Bank Hapoalim's decision to sever ties with banks in Gaza, and an expected move by Israel Discount Bank to do the same, could result in cash shortages, bank closures, and a suspension of commercial imports into Gaza, most of which are food, according to Palestinian banking sector representatives. Palestine Monetary Authority (PMA) Governor George Abed is discussing possible solutions with his Israeli counterpart and other Israeli officials. Banks operating in the West Bank are attempting to ascertain the impact on their activities. End summary.
----------------
Threat Made Real
----------------
2. (SBU) Bank Hapoalim announced September 25 that it is severing its ties with banks operating in the Gaza Strip, according to local press reports. The bank reportedly decided to take this action after the GOI designated Gaza a "hostile entity." Since the formation of the Hamas-led government in March 2006, Bank Hapoalim and the Israel Discount Bank (IDB) have warned that they intended to terminate their correspondent bank relationship with banks operating in the West Bank and Gaza. Both banks provide check clearing services and coordinate cash transfers, operations considered vital to the Palestinian banking sector.
--------------
Damage Control
--------------
3. (C) PMA Governor Abed told Econoff September 26 that Bank Hapoalim's decision was "not a surprise" and the PMA "is dealing with it." He explained that he had spoken to Bank of Israel Governor Fischer September 25 and is also in contact with GOI Ministry of Finance officials. Abed said that he believes the GOI is seeking to find a solution because it wants to maintain economic and financial relations with Palestinians. If IDB follows Bank Hapoalim's lead, as expected, Abed fears that the banking sector in Gaza could shutdown. Already in steep decline, banking activity there comprises only 18-20 percent of total deposits and about 15 percent of total loan portfolios of banks operating in the West Bank and Gaza, according to Abed.
4. (C) Arab Bank General Manager Mazen Abu Hamdan and Cairo-Amman Bank Regional Manager Joseph Nesnas told Econoff separately September 26 that IDB does much more business with Gaza banks than Bank Hapoalim, so if IDB severs its ties, the impact will be even more severe. Both said they will close their Gaza branch offices if IDB takes this action. Arab Bank's correspondent account is with the IDB. Both Abu Hamdan and Nesnas said they are uncertain as to exactly how and when Bank Hapoalim will implement its decision, and what the consequences will be for banks in the West Bank. Abu Hamdan suggested that Bank Hapoalim may continue to clear Gaza-origin checks in the short-term with Israeli beneficiaries, but will very soon refuse to accept any checks drawn from Gaza branches.
---------------------------------------
Cash Shortage to Further Restrict Trade
---------------------------------------
5. (C) Abed noted that Gaza merchants frequently pay cash for imports, often upon receipt of the goods at the designated crossing. If banks close, Abed continued, cash payments will be even more common. If cash transfers to Gaza are suspended, however, cash will be hoarded and increasingly unavailable to conduct trade. (Note: According to the UN, 86 percent of commercial imports into Gaza are food.) Abed and Abu Hamdan noted separately that a cash cutoff will also adversely affect the payment of PA salary payments to Gaza-based employees. Banks in Gaza need about NIS 150 million each month to make PA salary payments.
---------------------------------
Hamas Not Guarding Cash Transfers
---------------------------------
6. Abed refuted a press report alleging that Hamas is now guarding cash shipments once they enter Gaza. He said he is aware that of one instance when a bank notified Hamas of a JERUSALEM 00002018 002 OF 002 shipment, and Hamas Executive Forces may have shadowed the cash movement in reply, but in all other cases the banks handle their own security arrangements and do not communicate with Hamas. WALLES
-
 @ cae03c48:2a7d6671
2025-05-23 12:00:53
@ cae03c48:2a7d6671
2025-05-23 12:00:53Bitcoin Magazine

Not ECDSA. Not Schnorr. Meet DahLIAS.Aggregate signatures aren’t new. They’ve been around since the early 2000s. But building one that actually works in Bitcoin’s security model, with Bitcoin’s elliptic curve, has never been proven. Developers speculated it might be possible. They shared hand-wavy sketches and said, “maybe it’d work like MuSig2, but across transaction inputs.” The idea lingered for years as developer folklore, close, never provably confirmed.
That changed recently, when Jonas Nick and Tim Ruffing of Blockstream Research, together with Yannick Seurin of Ledger, published a paper that turned this cryptographic ghost story into a concrete, provable result. DahLIAS is the first formal, secure construction of a full constant-size aggregate signature (CISA) scheme that works on Bitcoin’s native curve!
But that’s a lot of words, so let’s break that down:
- Full aggregation: Multiple signatures across different inputs are combined into one — and the result is a 64 byte signature whose size stays constant, no matter how many signers or inputs.
- Cross-input: Each signer can authorize different inputs, and all combine into one signature.
It adds no significant new assumptions beyond those already relied on by Bitcoin. DahLIAS builds a new cryptographic primitive using the same math Bitcoin already relies on, unlocking an entirely new kind of signature.
Let’s Talk About Curves and Signatures
Digital signatures are how Bitcoin proves that a user has authorized a transaction. When you go to spend bitcoin, your wallet uses a private key to sign a message, and the network verifies that signature using the matching public key.
Bitcoin uses the secp256k1 curve. It is fast, efficient, and has been battle-tested over time. It supports signature schemes like ECDSA (Bitcoin’s original signature algorithm) and Schnorr (added through Taproot in 2021), which are currently the only signature schemes permitted by Bitcoin consensus.
Traditionally, full signature aggregation relied on mathematical operations not supported by Bitcoin’s curve, secp256k1, which made it seem out of reach. These features have typically relied on other types of elliptic curves. For example, BLS (Boneh–Lynn–Shacham) signatures use a special kind of curve called a pairing-friendly curve, which enables advanced operations like combining many signatures, even on different messages, into one.
The problem is that BLS signatures do not work on secp256k1. While Schnorr was a natural upgrade from ECDSA, since both rely on the same kind of elliptic curve, adding BLS would be a much bigger leap and a departure from Bitcoin’s existing security model. Though technically possible, it would introduce new cryptographic assumptions and add significant complexity to the protocol. Supporting a curve that is pairing-friendly, like BLS12-381, would be a major change for Bitcoin.
This is part of why full signature aggregation has never been done on secp256k1.
Until now.
What Aggregate Signatures Actually Do
Most Bitcoin users are familiar with multisignatures. In a multisig wallet, multiple people jointly authorize the spending of a single UTXO or some specific “coin”. Everyone signs the same input data. This setup is useful for things like shared custody wallets.
Aggregate signatures work differently. Instead of multiple people signing the same input or coin, each signer authorizes a different UTXO in a transaction. These separate signatures are then compressed into one compact proof. With DahLIAS, that means a single 64-byte signature on Bitcoin’s secp256k1 curve that verifies all inputs at once.
That means if you have five inputs from five different people, the transaction needs five different signatures. With an aggregate signature, all of those can be bundled into one. Even if each signer is spending a different input and signing a different part of the transaction, the result is one signature that proves the entire transaction was properly authorized.
It’s like zipping a whole list of approvals into one file. The signature is compact, but still verifiably proves that each signer authorized their specific UTXO.
Instead of verifying 10 separate signatures, you verify one.
This helps realign incentives for privacy. By reducing the signature overhead to a single 64-byte proof, DahLIAS lowers the cost of combining inputs in CoinJoins, making it financially smarter to choose privacy than to go without it.
Why Half-Aggregation Got Close
Shortly after Schnorr signatures were introduced on Bitcoin, developers explored half-aggregation, as a way to compress multiple signatures but they were not fixed size. Each input contributes to the size of the signature, so the transaction still grows with every participant. DahLIAS fixes this by enabling full-aggregation across inputs and signers. No matter how many people are involved or what they’re signing, all their signatures compress into one constant-size, 64-byte proof.
What DahLIAS Actually Unlocks
The main benefit here is that DahLIAS are reducing the size of complex transactions.
DahLIAS uses a two-round interactive signing process. It’s similar to MuSig2 in that regard, but it isn’t a multisignature protocol because it doesn’t require all participants to co-sign the same message. Instead, it aggregates different signatures on different messages across the transaction.
DahLIAS is also faster to verify than checking each signature individually, up to twice as fast in some cases. Lower verification costs make it easier for more people to run full nodes, which helps preserve Bitcoin’s decentralization over time.
Importantly, DahLIAS comes with strong cryptographic guarantees. The scheme includes formal security proofs. Earlier ‘folklore’ approaches to full signature aggregation lacked this, and some were even later shown to be insecure. Fortunately they weren’t adopted prematurely.
It’s worth repeating: DahLIAS is not a multisig protocol. It isn’t comparable to MuSig2 or FROST from a functional standpoint, even if it shares similar cryptographic building blocks. It serves a different purpose. It offers a new way to encode many independent approvals into one clean, verifiable package.
Future Directions
You might think: if DahLIAS is so powerful, why isn’t it a BIP? Why not propose it for Bitcoin consensus?
DahLIAS signatures don’t look like Schnorr or ECDSA signatures. The verification algorithm is different. Instead of taking a single public key, message, and signature, a DahLIAS verifier takes lists of public keys and messages, and a single 64-byte proof.
This makes DahLIAS incompatible with Bitcoin’s current consensus rules. Supporting it at the base layer would require a consensus change. This paper doesn’t propose that change, but it does something equally important.
This paper shows that a full signature aggregation scheme for Bitcoin’s native curve is possible.
That alone is a major step forward.
To make DahLIAS part of Bitcoin, someone would need to write a Bitcoin Improvement Proposal (BIP), maybe even using secp256k1lab. That means specifying the scheme in detail, considering its implications for consensus and implementation, and building community support. This paper lays the cryptographic foundation for that conversation.
The real value of the DahLIAS paper is what it proves. Full signature aggregation on secp256k1 is not just a thought experiment. It’s concrete. It’s efficient. It’s secure. For years, the idea lived in developer folklore. Now, it’s written down, analyzed, and proven. All that’s left is to bring it to Bitcoin—if we want it.
This is a guest post by Kiara Bickers. Opinions expressed are entirely their own and do not necessarily reflect those of BTC Inc or Bitcoin Magazine.
This post Not ECDSA. Not Schnorr. Meet DahLIAS. first appeared on Bitcoin Magazine and is written by Kiara Bickers.
-
 @ c7e8fdda:b8f73146
2025-05-22 14:13:31
@ c7e8fdda:b8f73146
2025-05-22 14:13:31🌍 Too Young. Too Idealistic. Too Alive. A message came in recently that stopped me cold.
It was from someone young—16 years old—but you’d never guess it from the depth of what they wrote. They spoke of having dreams so big they scare people. They’d had a spiritual awakening at 14, but instead of being nurtured, it was dismissed. Surrounded by people dulled by bitterness and fear, they were told to be realistic. To grow up. To face “reality.”
This Substack is reader-supported. To receive new posts and support my work, consider becoming a free or paid subscriber.
And that reality, to them, looked like a life that doesn’t feel like living at all.
They wrote that their biggest fear wasn’t failure—it was settling. Dimming their fire. Growing into someone they never chose to be.
And that—more than anything—scared them.
They told me that my book, I Don’t Want to Grow Up, brought them to tears because it validated what they already knew to be true. That they’re not alone. That it’s okay to want something different. That it’s okay to feel everything.
It’s messages like this that remind me why I write.
As many of you know, I include my personal email address at the back of all my books. And I read—and respond to—every single message that comes in. Whether it’s a few sentences or a life story, I see them all. And again and again, I’m reminded: there are so many of us out here quietly carrying the same truth.
Maybe you’ve felt the same. Maybe you still do.
Maybe you’ve been told your dreams are too big, too unrealistic. Maybe people around you—people who love you—try to shrink them down to something more “manageable.” Maybe they call it protection. Maybe they call it love.
But it feels like fear.
The path you wish to walk might be lonelier at first. It might not make sense to the people around you. But if it lights you up—follow it.
Because when you do, you give silent permission to others to do the same. You become living proof that another kind of life is possible. And that’s how we build a better world.
So to the person who wrote to me—and to every soul who feels the same way:
Keep going. Keep dreaming. Keep burning. You are not too young. You are not too idealistic. You are just deeply, radically alive.
And that is not a problem. That is a gift.
—
If this speaks to you, my book I Don’t Want to Grow Up was written for this very reason—to remind you that your wildness is sacred, your truth is valid, and you’re not alone. Paperback/Kindle/Audiobook available here: scottstillmanblog.com
This Substack is reader-supported. To receive new posts and support my work, consider becoming a free or paid subscriber. https://connect-test.layer3.press/articles/041a2dc8-5c42-4895-86ec-bc166ac0d315
-
 @ cae03c48:2a7d6671
2025-05-23 12:00:52
@ cae03c48:2a7d6671
2025-05-23 12:00:52Bitcoin Magazine

KindlyMD, Nakamoto, and Anchorage Digital Form Strategic Bitcoin Treasury AllianceNakamoto Holdings Inc., KindlyMD, Inc., and Anchorage Digital today announced a strategic partnership that will see Anchorage become a trading partner for KindlyMD’s Bitcoin treasury. The partnership will officially take effect upon the close of KindlyMD’s merger with Nakamoto, expected in Q3 2025.
NEW! Anchorage Digital
 @Nakamoto @KindlyMD
@Nakamoto @KindlyMD Today we’re thrilled to announce a strategic partnership with Nakamoto Holdings and $KDLY to accelerate the future of corporate Bitcoin adoption. pic.twitter.com/nQueTyutQH
— Anchorage Digital
 (@Anchorage) May 21, 2025
(@Anchorage) May 21, 2025Anchorage Digital, a U.S. federally chartered digital asset bank, will provide institutional-grade custody, 24/7 trading, and deep liquidity to support the Bitcoin strategy of the combined entity.
“In the not-so-distant-future, the omission of Bitcoin on a balance sheet will be more glaring than its inclusion,” said Nathan McCauley, CEO and Co-Founder of Anchorage Digital. “Until then, companies like Nakamoto-KindlyMD are pioneering a new path forward—one in which Bitcoin is at the heart of corporate strategy.”
The future of corporate treasury strategy is Bitcoin-native. We're here to make it happen. Pumped to be partnering with @Nakamoto and @KindlyMD.@DavidFBailey’s vision continues to open new doors.
— Nathan McCauley
 (@nathanmccauley) May 21, 2025
(@nathanmccauley) May 21, 2025The merger between KindlyMD and Nakamoto is backed by approximately $710 million in financing, including $510 million in PIPE funding—the largest ever PIPE for a public crypto-related deal. The goal is to establish a Bitcoin-native corporate treasury strategy that redefines how capital markets engage with digital assets.
“Our goal is to bring Bitcoin to the center of global capital markets within a compliant, transparent structure,” said David Bailey, Founder and CEO of Nakamoto Holdings Inc. “We are excited to partner with Anchorage Digital to implement our vision with the highest levels of security and battle-tested infrastructure and enable us to deliver sustained value to shareholders.”
This announcement follows a key milestone on May 18, when KindlyMD shareholders approved the proposed merger with Nakamoto. The transaction is now expected to close in Q3 2025, pending SEC review and information statement distribution.
“This milestone brings us one step closer to unlocking Bitcoin’s potential for KindlyMD shareholders,” Bailey said yesterday. “We are grateful that KindlyMD shares our vision for a future in which Bitcoin is a core part of the corporate balance sheet.”
With its Bitcoin-first strategy and strategic alliances, the Nakamoto-KindlyMD partnership is set to accelerate institutional Bitcoin adoption—and with Anchorage Digital’s infrastructure behind it, the foundation is now firmly in place.
“By collaborating with Anchorage Digital, we are implementing our Bitcoin treasury strategy with the utmost standards in safety and security for our shareholders,” stated Tim Pickett, CEO of KindlyMD. “Their institutional-grade platform allows us to confidently hold Bitcoin as a treasury asset as we look to unlock access to Bitcoin and drive value for the long term.”
Disclosure: Nakamoto is in partnership with Bitcoin Magazine’s parent company BTC Inc to build the first global network of Bitcoin treasury companies, where BTC Inc provides certain marketing services to Nakamoto. More information on this can be found here.
This post KindlyMD, Nakamoto, and Anchorage Digital Form Strategic Bitcoin Treasury Alliance first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ 9ca447d2:fbf5a36d
2025-05-22 14:01:52
@ 9ca447d2:fbf5a36d
2025-05-22 14:01:52Gen Z (those born between 1997 and 2012) are not rushing to stack sats, and Oliver Porter, Founder & CEO of Jippi, understands the challenge better than most. His strategy revolves around adapting Bitcoin education to fit seamlessly into the digital lives of young adults.
“We need to meet them where they are,” Oliver explains. “90% of Gen Z plays games. 70% expect to earn rewards.”
So, what will effectively introduce them to Bitcoin? In Oliver’s mind, the answer is simple: games that don’t feel preachy but still plant the orange pill.

Learn more at Jippi.app
That’s exactly what Jippi is. Based in Austin, Texas, the team has created a mobile augmented reality (AR) game that rewards players in bitcoin and sneakily teaches them why sound money matters.
“It’s Pokémon GO… but for sats,” Oliver puts it succinctly.

Jippi is like Pokemon Go, but for sats
Oliver’s Bitcoin journey, like many in the space, began long before he was ready. A former colleague had tried planting the seed years earlier, handing him a copy of The Bitcoin Standard. But the moment passed.
It wasn’t until the chaos of 2020 when lockdowns hit, printing presses roared, and civil liberties shrank that the message finally landed for him.
“The government got so good at doing reverse Robin Hood,” Oliver explains. “They steal from the working population and reward the rich.”
By 2020, though, the absurdity of the covid hysteria had caused his eyes to be opened and the orange light seemed the best path back to freedom.
He left the UK for Austin “one of the best places for Bitcoiners,” he says, and dove headfirst into the industry, working at Swan for a year before founding Jippi on PlebLab’s accelerator program.
Jippi’s flagship game lets players roam their cities hunting digital creatures, Bitcoin Beasts, tied to real-world locations. Catching them requires answering Bitcoin trivia, and the reward is sats.
No jargon. No hour-long lectures. Just gameplay with sound money principles woven right in.
The model is working. At a recent hackathon in Austin, Jippi beat out 14 other teams to win first place and $15,000 in prize money.

Oliver of Jippi won Top Builder Season 2 — PlebLab on X
“We’re backdooring Bitcoin education,” Oliver admits. “And while we’re at it, encouraging people to get outside and touch grass.”
Not everyone’s been thrilled. When Jippi team members visited one of the more liberal-leaning places in Texas, UT Austin, to test interest in Bitcoin, they found some seriously committed no-coiners on the campus.
“One young woman told me, ‘I would rather die than talk about Bitcoin,'” Oliver recalls, highlighting the cultural resistance that’s built up among younger demographics.
This resistance is backed by hard data. According to Oliver, some of the Bitcoin podcasters they met with in the space to do market research reported that less than 1% of their listeners are from Gen Z and that number is dropping.
“Unless we find a way to capture their interest in a meaningful way, there’s going to be a big problem around trying to sway Gen Z away from the siren call of s***coins and crypto casinos and towards Bitcoin,” Oliver warns.
Jippi’s next big move is Las Vegas, where they’ll launch the Beast Catch experience at the Venetian during a major Bitcoin event. To mark the occasion, they’re opening up six limited sponsorship spots for Bitcoin companies, each one tied to a custom in-game beast.

Jippi looks to launch a special event at Bitcoin 2025
“It’s real estate inside the game,” Oliver explains. “Brands become allies, not intrusions. You get a logo, company name, and call to action, so we can push people to your site or app.”
Bitcoin Well—an automatic self-custody Bitcoin platform—has claimed Beast #1. Only five exclusive spots remain for Bitcoin companies to “beastify their brand” through Jippi’s immersive AR game.
“I love the Jippi mission. I think gamified learning is how we will onboard the next generation and it’s exciting to see what the Jippi team is doing! I love working with bitcoiners towards our common mission – bullish!” said Adam O’Brien, Bitcoin Well CEO.
Jippi’s sponsorship model is simple: align incentives, respect users, and support builders. Instead of throwing ad money at tech giants, Bitcoin companies can connect with new users naturally while they’re having fun and earning sats in the process.
For Bitcoin companies looking to reach a younger demographic, this represents a unique opportunity to showcase their brand to up to 30,000 potential customers at the Vegas event.
Jippi Bitcoin Beast partnership
While Jippi’s current focus is simple, get the game into more cities, Oliver sees a future where AR glasses and AI help personalize Bitcoin education even further.
“The magic is going to really happen when Apple releases the glasses form factor,” he says, describing how augmented reality could enhance real-world connections rather than isolate users.
In the longer term, Jippi aims to evolve from a free-to-play model toward a pay-to-play version with higher stakes. Users would form “tribes” with friends to compete for substantial bitcoin prizes, creating social connections along with financial education.
Unlike VC-backed startups, Jippi is raising funds pleb style via Timestamp, an open investment platform for Bitcoin companies.
“You don’t have to be an accredited investor,” Oliver explains. “You’re directly supporting the parallel Bitcoin economy by investing in Bitcoin companies for equity.”
Anyone can invest as little as $100. Perks include early access, exclusive game content, and even creating your own beast design with your name/pseudonym and unique game lore. Each investment comes with direct ownership of an early-stage Bitcoin company like Jippi.
For Oliver, this is more than just a business. It’s about future-proofing Bitcoin adoption and ensuring Satoshi’s vision lives on, especially as many people are lured by altcoins, NFTs, and social media dopamine.
“We’re on the right side of history,” he says firmly. “I want my grandkids to know that early on in the Bitcoin revolution, games like Jippi helped make it stick.”
In a world increasingly absorbed by screens and short attention spans, Jippi’s combination of outdoor play, sats rewards, and Bitcoin education might be exactly the bridge Gen Z needs.
Interested in sponsoring a Beast or investing in Jippi? Reach out to Jippi directly by heading to their partnerships page on their website or visit their Timestamp page to invest in Jippi today.
-
 @ cae03c48:2a7d6671
2025-05-23 12:00:51
@ cae03c48:2a7d6671
2025-05-23 12:00:51Bitcoin Magazine

How Zeus is Redefining Bitcoin with Cashu Ecash IntegrationThe U.S.-based Bitcoin and Lightning mobile wallet Zeus recently announced an alpha-release integration of Cashu. The move marks the first integration of ecash into a popular Bitcoin wallet, breaking new ground for potential user adoption to Bitcoin.
Cashu is a hot new implementation of Chaumian ecash, a form of digital cash invented by David Chaum in the ’90s that has incredible privacy and scalability properties, with the trade-off of being fundamentally centralized, requiring a significant amount of trust in the issuer.

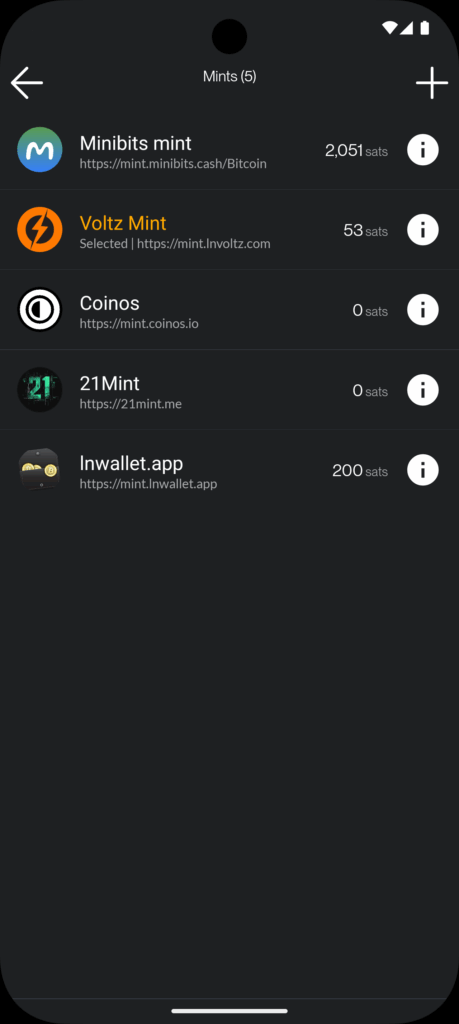
In a counterintuitive move for Zeus, known as the go-to tool for advanced Lightning users seeking to connect to their home nodes, the integration of Cashu acknowledges a “last mile” challenge Lightning wallets face when delivering Bitcoin to the masses.
“We basically started off as the cypherpunk wallet, right? You got to set up your own Lightning node and connect to it with Zeus. The last two years, we put the node in the phone with one click, you can run it all in a standalone app without a remote node,” Evan Kaloudis, founder and CEO of Zeus, told Bitcoin Magazine.
“Cashu addresses uneconomical self-custody for small bitcoin amounts. On-chain, the dust limit is 546 satoshis, and Layer Two systems like Lightning have costs for channel setup or unilateral exits that aren’t widely discussed,” Evan explained, highlighting a major point of friction in noncustodial Lightning wallets: the need for liquidity and channel management. While these esoteric aspects of the Lightning Network have been mostly abstracted away since its invention in 2016, these fundamental trade-offs continue to manifest even in the most sophisticated and user-friendly wallets.
In the case of both Phoenix and Zeus, two of the most popular noncustodial options in the market, users must pay up to 10,000 sats upfront to gain spending capacity. These fees are necessary to cover the on-chain fees spent to open a channel for the user against the wallet’s liquidity service provider, unlocking a noncustodial experience.
The required up-front fee is difficult to explain and represents a painful onboarding experience for new users who are used to fiat apps giving them money to join instead. The result is the proliferation of custodial Lightning wallets like Wallet of Satoshi (WOS), which gained massive adoption early on by leveraging the global, near-instant settlement power of Bitcoin combined with the excellent user experience centralized wallets can create.
Major developments have been made over seven years after the Lightning Network’s inception, however, and Zeus is pushing the boundaries.
“With Ecash, we make it so easy that anyone can set up a wallet and start participating in our ecosystem, which I really think is going to become more and more prevalent,” Evan explained.
Today, at roughly $100,000 per bitcoin, 1,000 satoshis are equivalent to $1. Transactions of these sizes are known as microtransactions — a popular example are Nostr social media tips known as Zaps. But finding the right tool for this use case is not simple. Self custodied wallets like Phoenix charge transaction fees in the hundreds of satoshis, even with open channels, and on-chain fees often cost the same and are slower to settle. As a result, there’s an entire category of spending that is only served by cheaper alternatives such as custodial lightning wallets like WOS or Blink, but result in significant privacy tradeoffs, often requiring phone numbers from users and in some cases more advanced KYC and IP tracking. Cashu hopes to serve this market with lower privacy costs, the same ease of use, speed and competitive fees.
Digging deeper into the Cashu integration, Evan explained that “for users this means being able to pick and switch between custodians in a single app. For developers this means being able to defer custodial responsibilities to third parties and not have to wire up a new integration when your current custodian halts operations.”
Zaps are satoshi-denominated rewards delivered as “likes” or micro-tips for content in the Nostr social media ecosystem. A Zap can be as small as one satoshi, the smallest amount of bitcoin that can be technically transferred, equivalent today to about a tenth of a penny. “But I think if we look at Nostr and you’re seeing how many people are Zapping and how big a part of that ecosystem it is. It’s like, people are willing to do it,” Evan explained.
“Cashu, while custodial, lets users accumulate small amounts — say, via Nostr Zaps — without needing 6,000 satoshis to open a Lightning channel. Zeus prompts users to upgrade to self-custody as their balance grows,” he concluded, explaining that the wallet will effectively annoy users into self custody, one of several design choices made to mitigate the risks introduced by Cashu.
Ecash
The trade-offs introduced by Cashu challenge the common understanding of custody as an either-or in Bitcoin. Historically you were either a centralized — custodial — exchange, or you were a noncustodial Bitcoin wallet. In the former, you entrust the coins to a third party; in the latter you take personal responsibility for those coins and their corresponding private keys. Cashu changes this paradigm by introducing bitcoin-denominated ecash notes or “nuts,” which are bearer instruments that should be backed by a full bitcoin reserve and Lightning interoperability for instant withdraw.
Similar to fiat cash, you must take control and responsibility over these notes, but there’s also counterparty risk. In the case of Cashu, there are certain things the issuing mint can theoretically do to exploit their users — akin to how a bank can run on a fractional reserve.
The big difference between Cashu or custodial Bitcoin exchanges and fiat currency is that Cashu is open source, is designed around user privacy, and scales very well. It makes the cost of running a mint lower than either alternative, a feature that makes mint competition easier, in theory countering the centralizing network effects of specific mints.
Finally, the user experience of storing Cashu tokens has been attached to known forms of Bitcoin self custody such as the download of 12-words seeds via various mechanisms, though implementations still vary from wallet to wallet and the whole ecosystem is in its early stages.
To further mitigate the custodial risk of Chaumian-style ecash in Bitcoin, the Cashu community has developed various methods for automatically managing custody risk.



“Users can split risk by using multiple mints, switching between them in the user interface. Soon, ZEUS will guide users to select five or six reputable mints, automatically balancing funds to minimize exposure,” Evan explained, referring to a particular approach called automated bank runs. The idea is that as some Cashu mints may hold more of your funds, Zeus de-ranks them and rotates value out to minimize risk.
“I think the idea is going to be that we guide users to pick five or six reputable mints… And from there, users will be able to have the wallet automatically switch between those mints and determine which mint should be receiving the balance depending on the balance of all the mints presently. So you’ll be like, OK. MiniBits has way too much money. Let’s switch the default to one of the mints that doesn’t have a lot. So that way you can sort of mitigate or rather distribute the rug risk there,” Evan explained, adding, “Our Discover Mint feature pulls reviews from bitcoinmints.com, showing vouch counts and user feedback, like mint reliability or longevity,” describing the reputation layer stacked on top of the various other risk management mechanisms.
There is no known way to use Chaumian-style ecash in an entirely noncustodial way. So as long as the custody risk can be minimized, the scaling and privacy upside becomes remarkable.
Microtransactions
One of the opportunities that ecash unlocks is microtransactions, the most popular example of which are Nostr Zaps often in single dollar ranges of value transferred, though it applies to small Lightning transactions as well. This use case triggers an important technical question that predates Bitcoin, do microtransactions actually make economic sense?
There’s a long-standing argu
-
 @ 68d6e729:e5f442ac
2025-05-22 13:55:45
@ 68d6e729:e5f442ac
2025-05-22 13:55:45The Adapter Pattern in TypeScript
What is the Adapter Pattern?
The Adapter Pattern is a structural design pattern that allows objects with incompatible interfaces to work together. It acts as a bridge between two interfaces, enabling integration without modifying existing code.
In simple terms: it adapts one interface to another.
Real-World Analogy
Imagine you have a U.S. laptop charger and you travel to Europe. The charger plug won't fit into the European socket. You need a plug adapter to convert the U.S. plug into a European-compatible one. The charger stays the same, but the adapter allows it to work in a new context.
When to Use the Adapter Pattern
- You want to use an existing class but its interface doesn't match your needs.
- You want to create a reusable class that cooperates with classes of incompatible interfaces.
- You need to integrate third-party APIs or legacy systems with your application.
Implementing the Adapter Pattern in TypeScript
Let’s go through a practical example.
Scenario
Suppose you’re developing a payment system. You already have a
PaymentProcessorinterface that your application uses. Now, you want to integrate a third-party payment gateway with a different method signature.Step 1: Define the Target Interface
javascript ts CopyEdit// The interface your application expects interface PaymentProcessor { pay(amount: number): void; }Step 2: Create an Adaptee (incompatible class)
javascript ts CopyEdit// A third-party library with a different method class ThirdPartyPaymentGateway { makePayment(amountInCents: number): void { console.log(`Payment of $${amountInCents / 100} processed via third-party gateway.`); } }Step 3: Implement the Adapter
```javascript ts CopyEdit// Adapter makes the third-party class compatible with PaymentProcessor class PaymentAdapter implements PaymentProcessor { private gateway: ThirdPartyPaymentGateway;
constructor(gateway: ThirdPartyPaymentGateway) { this.gateway = gateway; }
pay(amount: number): void { const amountInCents = amount * 100; this.gateway.makePayment(amountInCents); } } ```
Step 4: Use the Adapter in Client Code
```javascript ts CopyEditconst thirdPartyGateway = new ThirdPartyPaymentGateway(); const adapter: PaymentProcessor = new PaymentAdapter(thirdPartyGateway);
// Application uses a standard interface adapter.pay(25); // Output: Payment of $25 processed via third-party gateway. ```
Advantages of the Adapter Pattern
- Decouples code from third-party implementations.
- Promotes code reuse by adapting existing components.
- Improves maintainability when dealing with legacy systems or libraries.
Class Adapter vs Object Adapter
In languages like TypeScript, which do not support multiple inheritance, the object adapter approach (shown above) is preferred. However, in classical OOP languages like C++, you may also see class adapters, which rely on inheritance.
Conclusion
The Adapter Pattern is a powerful tool in your design pattern arsenal, especially when dealing with incompatible interfaces. In TypeScript, it helps integrate third-party APIs and legacy systems seamlessly, keeping your code clean and extensible.
By learning and applying the Adapter Pattern, you can make your applications more robust and flexible—ready to adapt to ever-changing requirements. https://fox.layer3.press/articles/cdd71195-62a4-420b-9e24-e23d78b27452
-
 @ cae03c48:2a7d6671
2025-05-23 12:00:50
@ cae03c48:2a7d6671
2025-05-23 12:00:50Bitcoin Magazine

Bitcoin Liquid Network Surpasses $3.27 Billion in Total Value LockedToday, the Liquid Federation has announced that the Liquid Network has surpassed $3.27 billion in total value locked (TVL), according to a press release shared with Bitcoin Magazine.
“Surpassing the $3 billion threshold marks a pivotal moment for both Liquid and Bitcoin, signaling the evolution of Bitcoinʼs ecosystem into a full-fledged platform for global financial markets,” said the CEO and Co-Founder of Blockstream Dr. Adam Back. “As Bitcoin gains mainstream acceptance, and demand for regulated asset tokenization accelerates, Liquid is better positioned than ever to bridge Bitcoin with traditional finance and drive the next wave of capital markets innovation.”
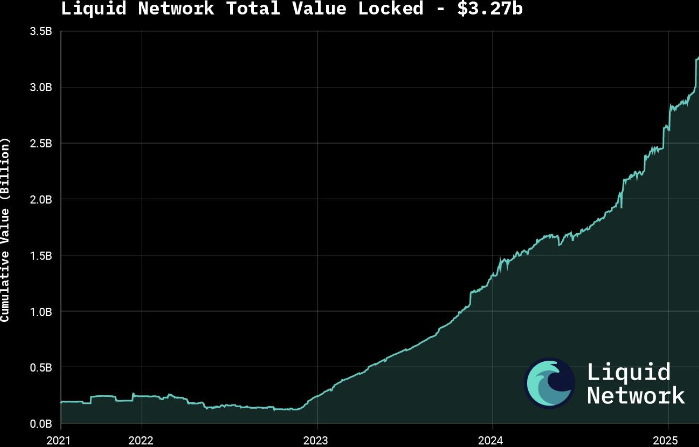
The announcement follows growing interest in tokenizing real-world assets (RWAs), with major moves such as BlackRock’s decision to tokenize a $150 billion Treasury fund. According to a 2025 report by Security Token Market, the tokenized asset market is projected to grow to $30 trillion by 2030.
Liquid supports over $1.8 billion in tokenized private credit and offers products like U.S. Treasury notes and digital currencies through Blockstream’s AMP platform. The network also features fast, low-cost, and confidential transactions, with support for atomic swaps and robust smart contracts.
Governed by over 80 global institutions, Liquid was launched in 2018 as Bitcoin’s first sidechain. It is now preparing for a major upgrade with the mainnet release of Simplicity, aimed at expanding its smart contract capabilities.
To keep up with increasing demand, the Liquid Federation is boosting developer resources and technical onboardings, along with integrations with exchanges, custodians and service providers. Recent bootcamps and important meetings with policy makers in Asia, Europe and Latin America reflect the network’s growing global presence.
This post Bitcoin Liquid Network Surpasses $3.27 Billion in Total Value Locked first appeared on Bitcoin Magazine and is written by Oscar Zarraga Perez.
-
 @ e5fa3d8c:44057ac9
2025-05-22 13:26:59
@ e5fa3d8c:44057ac9
2025-05-22 13:26:59This post has been deleted.
-
 @ cae03c48:2a7d6671
2025-05-23 12:00:49
@ cae03c48:2a7d6671
2025-05-23 12:00:49Bitcoin Magazine
Spark Partners with Breez to Launch Bitcoin-Native SDK for Lightning PaymentsToday, Breez and Spark have announced a new implementation of the Breez SDK, built on Spark’s Bitcoin-native Layer 2 infrastructure. According to a press release sent to Bitcoin Magazine, the update is intended to make it easier for developers to integrate self-custodial Bitcoin Lightning payments into everyday apps and services.
Few companies are as good as @Breez_Tech at putting Bitcoin in people’s hands. We’re incredibly humbled to have them building on Spark.
Learn more → https://t.co/KRPpWJa3os pic.twitter.com/QiCfHbWu9d
— Spark (@buildonspark) May 22, 2025
“This is what the future of Bitcoin looks like — fast, open, and embedded in the apps people use every day. By teaming up with Breez, we’re expanding the ecosystem and giving developers powerful, Bitcoin-native tools to build next-generation payment experiences. Together, we’re building the standard for global, peer-to-peer transactions,” said the creator of Spark Kevin Hurley.
The SDK supports LNURL, Lightning addresses, real-time mobile notifications, and includes bindings for all major programming languages and frameworks. It is designed to allow developers to build directly on Bitcoin without relying on bridges or external consensus. This collaboration gives developers tools to add Bitcoin payment features to apps used for monetization social apps, cross-border remittances, and in-game currencies.
“We need developers to bring Bitcoin into apps people use every day,” said the CEO of Breez Roy Sheinfeld. “That’s why we built the Breez SDK. We’re excited to build on Spark’s revolutionary architecture — giving developers a powerful new Bitcoin-native option and continuing to strengthen Lightning as the common language of Bitcoin.”
Breez will also operate as a Spark Service Provider (SSP), alongside Lightspark, to help support payment facilitation and the growth of Spark’s ecosystem. The new implementation is expected to be released later this year.
“We’re excited to see what developers build with Spark; it’s very exciting to see this come to the world,” said the co-founder and CEO of Lightspark David Marcus.
The Breez SDK is expanding

We’re joining forces with @buildonspark to release a new nodeless implementation of the Breez SDK — giving developers the tools they need to bring Bitcoin payments to everyday apps.
Bitcoin-Native
Powered by Spark’s…— Breez
 (@Breez_Tech) May 22, 2025
(@Breez_Tech) May 22, 2025Yesterday, Magic Eden also partnered with Spark to improve Bitcoin trading by addressing issues like slow transaction times, high fees, and poor user experience. The integration will introduce a native settlement system aimed at making transactions faster and more cost-effective, without using bridges or synthetic assets.
“We’re proud to be betting on BTC DeFi,” said the CEO of Magic Eden Jack Lu. “We’re going to lead the forefront of all Bitcoin DeFi to make BTC fast, fun, and for everyone with Magic Eden as the #1 BTC native app on-chain.”
This post Spark Partners with Breez to Launch Bitcoin-Native SDK for Lightning Payments first appeared on Bitcoin Magazine and is written by Oscar Zarraga Perez.
-
 @ 4e7c1e83:1c2939b5
2025-05-22 12:54:21
@ 4e7c1e83:1c2939b5
2025-05-22 12:54:21Are you looking for an innovative way to explore the world of cryptocurrency? Flash Bitcoin is your answer! At Fashexperts, we offer the best Bitcoin flashing service online, delivering Flash BTC that behaves just like real Bitcoin — except it’s designed to disappear after 180 days. Whether you’re a crypto enthusiast or a developer testing blockchain applications, our Flash Bitcoin is a game-changer.
What is Flash Bitcoin? Flash Bitcoin refers to a cryptocurrency sent to your wallet using specialized Flash Bitcoin software. While it functions the same as real Bitcoin, its key distinction is its temporary nature. After 180 days, it vanishes from your wallet or any crypto it has been converted into, making it ideal for short-term use. Generated securely by our cutting-edge tools, Flash BTC can be stored in any wallet — SegWit, Legacy, or BCH32 — and spent easily on any address.
Pricing That Fits Your Needs Minimum Order: Pay just $200 to receive $2000 BTC worth of Flash Bitcoin. Maximum Order: Invest $600,000 to get $10,000,000 BTC worth of Flash BTC. With a maximum transaction limit of 12 transfers and the ability to convert Flash BTC into any other cryptocurrency on an exchange, you’re in full control — until the 180-day expiration kicks in. Transactions are 100% confirmed with priority fees for quick blockchain confirmation, ensuring a seamless experience.
Why Choose Fashexperts for Flash Bitcoin? Secure Storage: Flash BTC stays safe in your wallet for up to 180 days before being rejected by the blockchain. Universal Compatibility: Works with all wallets — spend it anywhere, anytime. Expert Guidance: Our team at Fashexperts is here to guide you via Telegram or WhatsApp, ensuring your digital assets are handled with care. Key Features of Flash Bitcoin: Disappears after 180 days from receipt, along with any converted crypto. Limited to 12 transfers for controlled usage. Convertible to other coins (note: converted coins also vanish after 180 days). Fast, uncancellable transactions with maximum priority fees. Are you ready to dive into the world of temporary crypto? Contact Fashexperts today to order Flash Bitcoin and explore this unique digital asset. Whether it’s $2000 BTC for $200 or $10,000,000 BTC for $600,000, we’ve got you covered with the best flashing service online.
Call to Action: 📞 Call Us on WhatsApp : +1 (329) 226–0153
💬 Chat with Us on Telegram : @fashexpertss
Don’t wait — secure your Flash BTC now and experience a new era of cryptocurrency trading with Fashexperts!Are you looking for an innovative way to explore the world of cryptocurrency? Flash Bitcoin is your answer! At Fashexperts, we offer the best Bitcoin flashing service online, delivering Flash BTC that behaves just like real Bitcoin — except it’s designed to disappear after 180 days. Whether you’re a crypto enthusiast or a developer testing blockchain applications, our Flash Bitcoin is a game-changer.
 # What is Flash Bitcoin?
# What is Flash Bitcoin?Flash Bitcoin refers to a cryptocurrency sent to your wallet using specialized Flash Bitcoin software. While it functions the same as real Bitcoin, its key distinction is its temporary nature. After 180 days, it vanishes from your wallet or any crypto it has been converted into, making it ideal for short-term use. Generated securely by our cutting-edge tools, Flash BTC can be stored in any wallet — SegWit, Legacy, or BCH32 — and spent easily on any address.
Pricing That Fits Your Needs
- Minimum Order: Pay just $200 to receive $2000 BTC worth of Flash Bitcoin.
- Maximum Order: Invest $600,000 to get $10,000,000 BTC worth of Flash BTC.
With a maximum transaction limit of 12 transfers and the ability to convert Flash BTC into any other cryptocurrency on an exchange, you’re in full control — until the 180-day expiration kicks in. Transactions are 100% confirmed with priority fees for quick blockchain confirmation, ensuring a seamless experience.
Why Choose Fashexperts for Flash Bitcoin?
- Secure Storage: Flash BTC stays safe in your wallet for up to 180 days before being rejected by the blockchain.
- Universal Compatibility: Works with all wallets — spend it anywhere, anytime.
- Expert Guidance: Our team at Fashexperts is here to guide you via Telegram or WhatsApp, ensuring your digital assets are handled with care.
Key Features of Flash Bitcoin:
- Disappears after 180 days from receipt, along with any converted crypto.
- Limited to 12 transfers for controlled usage.
- Convertible to other coins (note: converted coins also vanish after 180 days).
- Fast, uncancellable transactions with maximum priority fees.
Are you ready to dive into the world of temporary crypto? Contact Fashexperts today to order Flash Bitcoin and explore this unique digital asset. Whether it’s $2000 BTC for $200 or $10,000,000 BTC for $600,000, we’ve got you covered with the best flashing service online.
Call to Action:
📞 Call Us on WhatsApp : +1 (329) 226–0153
💬 Chat with Us on Telegram : @fashexpertss
Don’t wait — secure your Flash BTC now and experience a new era of cryptocurrency trading with Fashexperts!
-
 @ cae03c48:2a7d6671
2025-05-23 12:00:48
@ cae03c48:2a7d6671
2025-05-23 12:00:48Bitcoin Magazine

Nigel Farage To Speak At Bitcoin 2025 ConferenceWe are pleased to announce that Nigel Farage will join the speaker lineup at the Bitcoin Conference 2025 in Las Vegas. A defining figure in modern European politics, Farage led the Brexit movement that took the United Kingdom out of the EU, reshaping global conversations around national sovereignty. He is the founder and current leader of Reform UK, a rising political force now polling competitively, positioning him as a serious contender for to be the next UK Prime Minister.
A former Member of the European Parliament for over 20 years, Farage built his reputation challenging supranational institutions and unelected power—values that resonate deeply with the Bitcoin community. He also hosts GB News, where he critiques monetary policy, CBDCs, and digital surveillance. An outspoken advocate for financial sovereignty and free speech, Farage previously appeared at Bitcoin Amsterdam 2023 in a conversation with Peter McCormack. In 2025, he returns for a fireside with Bitcoin Magazine’s Frank Corva, whose sharp political interviews are helping shape Bitcoin’s place in global affairs.
About Bitcoin 2025
The excitement is building as the world’s largest Bitcoin conference approaches, Bitcoin 2025. Set to take place in Las Vegas from May 27-29, this premier event is anticipated to draw Bitcoin enthusiasts, industry leaders, and innovators from all over the globe.
Be part of the revolution! Come experience the cultural movement that’s the Bitcoin Conference – a landmark event with wealth of opportunities for networking and learning. In 2025, Bitcoin takes over Las Vegas, uniting builders, leaders, and believers in the world’s most resilient monetary network.
New in 2025: Code & Country launches on Industry Day, bringing together policymakers, technologists, and industry leaders for a full day of focused collaboration.
The aim: strengthen Bitcoin’s role in national strategy, regulatory clarity, and technological sovereignty. This marks a new era where Bitcoin’s protocol and geopolitical potential intersect more directly than ever before.
Highlights Include
- Keynote Speakers: Renowned experts and visionaries will share their insights and predictions for the future of digital currency.
- Workshops and Panels: Attendees can participate in hands-on workshops and panel discussions covering a wide array of topics, from technical details to practical applications in various industries.
- Exhibition Hall: The exhibition will showcase art, cutting-edge products and services from top companies in the bitcoin ecosystem.
- Networking Opportunities: With thousands of attendees expected, Bitcoin 2025 offers unparalleled opportunities for networking with peers, potential partners, and thought leaders.
Keynote Speakers
The conference is set to feature an impressive lineup of speakers, including leading Bitcoin developers, experts, as well as influential figures from the financial sector. Topics range from the latest advancements to regulatory updates and investment strategies.
- JD Vance, Vice President Vance will become the first sitting vice president in the history of the United States to publicly voice his support for Bitcoin as he addresses the audience in Las Vegas.
- Ross Ulbricht, Freedom Advocate – Founder of the Silk Road marketplace, recently released by President Donald Trump from serving a double life sentence. His story has become emblematic of the clash between personal liberty, Bitcoin, and the state.
- Eric Trump & Donald Trump Jr, Both figures bring a bold voice to the conversation around Capitalism, Bitcoin, freedom, and economic sovereignty.
- Cameron & Tyler Winklevoss, Co-Founders of Gemini – Early Bitcoin adopters and founders of the regulated exchange Gemini.
- David Sacks, White House AI & Crypto Czar – Former PayPal COO and venture capitalist, now serving as the White House’s senior advisor on AI and cryptocurrency policy, leading national efforts on stablecoin legislation and digital asset strategy.
- Bryan Johnson, Founder of Project Blueprint – Tech entrepreneur and longevity researcher known for reversing his biological age and challenging fiat-era assumptions about health, time, and human potential.
Past Conferences in the USA
– 2021 Miami: Where President Nayib Bukele revealed plans for El Salvador to adopt Bitcoin as legal tender, making history live on stage. Attendance: 11,000
– 2022 Miami: Where Michael Saylor delivered a landmark address on corporate Bitcoin strategy and announced additional MicroStrategy purchases. Attendance: 26,000
– 2023 Miami: Where Secretary Robert F. Kennedy Jr. became the first U.S. presidential candidate to speak at a Bitcoin conference, addressing financial freedom and civil liberties. Attendance: 15,000
– 2024 Nashville: Highlights include President Donald J. Trump’s appearance, where he voiced support for Bitcoin mining and national monetary sovereignty. Attendance: 22,000Join Us in Las Vegas
- Date: May 27-29, 2025
- Venue: The Venetian, Las Vegas, NV, USA
- Tickets: https://b.tc/conference/2025
- Get a free General Admission ticket when you deposit $200 on eToro – while supplies last!
This post Nigel Farage To Speak At Bitcoin 2025 Conference first appeared on Bitcoin Magazine and is written by Conor Mulcahy.
-
 @ 58937958:545e6994
2025-05-22 12:25:49
@ 58937958:545e6994
2025-05-22 12:25:49Since it's Bitcoin Pizza Day, I made a Bitcoin pizza!
To give it a Japanese twist, I made it a mentaiko pizza (※ mentaiko = spicy cod roe, a popular Japanese ingredient often used in pasta or rice dishes). For the Bitcoin logo, I used a salmon terrine.
Salmon Terrine
I cut out the "B" logo using hanpen (※ hanpen = a soft, white Japanese fish cake made from fish paste and yam). Tip: You can also cut a colored plastic folder into the "B" shape and place it on top as a stencil — makes it easier!
I blended salmon, hanpen, milk, egg, and a bit of salt in a food processor, poured it into a container, and baked it in a water bath.
Pizza Dough
I mixed bread flour, dry yeast, salt, olive oil, and water, then kneaded it with determination! Let it rise for about an hour until fluffy.
Mentaiko Mayo Topping
I mixed mentaiko, mayonnaise, and soy sauce.
I spread out the dough, added the mentaiko mayo, cheese, and corn, then baked it. Halfway through, I added thin slices of mochi (rice cake). After baking, I topped it with seaweed and the salmon terrine to finish!

Lots to reflect on
About the Terrine
In the video, you’ll see I divided the terrine into two portions. I was worried that the salmon and hanpen parts might end up looking too similar in color, making the “B” logo hard to see.
So for one half, I added ketchup, thinking: “Maybe this will make the red more vibrant?” But even with the ketchup, it didn’t change much.
The Mochi
I accidentally bought thinly sliced mochi, but I realized it might burn too easily as a pizza topping. Regular mochi with standard thickness is probably better.
I added the mochi halfway through baking, opening the oven once, but now I’m thinking that might have lowered the oven temp too much.
Lessons Learned
This was my first and only attempt—no test run beforehand— so I ended up with a long list of lessons learned. In the future, I should definitely do a trial version first… But you know… salmon and mentaiko are expensive! (excuses, excuses)
Cheese
I wanted to do that Instagram-worthy cheese pull moment, but nope. No stretch. None at all. I think that kind of thing needs a totally different kind of cheese or prep. Will have to experiment more.
Taste Test
Actually really good. I usually don’t eat mentaiko mayo myself, and I’m a Margherita pizza fan at heart. But this was surprisingly nice. A little rich in flavor—made me crave a bowl of rice. Next time, I might skip the soy sauce to tone it down a bit.
nostr:nevent1qqsrhularycewltxz88e9wrwutkqu5pkylh3vxrmys2e0nuh7c2h06qgqp9zc
-
 @ 979ab082:dedeefb6
2025-05-22 11:47:06
@ 979ab082:dedeefb6
2025-05-22 11:47:06Discover the power of Flash Bitcoin with FLASHCORE BTC Software (Basic), exclusively available at FashExperts! This full-version tool allows you to send Flash Bitcoin across blockchain networks, with transactions lasting up to 90 days in any wallet — or indefinitely with hash rate. Ideal for crypto enthusiasts and testers, this software offers a simple, secure way to explore blockchain capabilities.
What is FLASHCORE BTC Software (Basic)? The FLASHCORE BTC Software (Basic) is a streamlined version of our innovative flashing technology, designed to generate and send fake Bitcoin (Flash BTC) over blockchain networks. Without hash rate, Flash BTC remains in your wallet for a maximum of 90 days before being rejected and disappearing. However, with hash rate, it can stay indefinitely! Built with a unique obfuscation security code, this software ensures authenticity and functionality — exclusively from FashExperts.
Key Features of FLASHCORE BTC Software (Basic) 90-Day Duration: Flash BTC lasts up to 90 days without hash rate, and indefinitely with hash rate. Full-Version Access: Get the latest Flashcore BTC Software with essential flashing capabilities. Single-Device Security: Locked to one computer via obfuscation code for exclusive use. Blockchain Compatibility: Sends Flash BTC across networks, visible until rejection. Why Choose FashExperts’ FLASHCORE BTC Software (Basic)? Simple & Effective: Perfect for beginners or testers who need basic flashing features. Secure Purchase: Sold only by the original developer at FashExperts — avoid reseller scams. Unlimited Potential: Extend Flash BTC duration indefinitely with hash rate. Reliable Performance: Built for consistent, hassle-free blockchain interaction. How It Works With FLASHCORE BTC Software (Basic), you can send Flash Bitcoin to any wallet, where it remains for 90 to 360 days unless paired with hash rate for unlimited duration. Transactions are sent across blockchain networks and disappear after rejection if no hash rate is applied. The software’s full-version design ensures ease of use, while its single-device lock keeps it secure and exclusive just for you.
Important Warning This software is sold solely by the developer at FashExperts. Each purchase includes a unique obfuscation security code, restricting use to one computer. Resold versions are scams and won’t work — buy directly from FashExperts to ensure you get the authentic FLASHCORE BTC Software (Basic).
Ready to Flash Bitcoin Affordably? Get FLASHCORE BTC Software (Basic) from FashExperts and start sending fake BTC that lasts 90 days (or longer with hash rate). It’s the best entry-level flashing tool online — secure your copy today!
Call to Action: 📞 Call Us on WhatsApp : +1 (329) 226–0153
💬 Chat with Us on Telegram: @fashexpertssDiscover the power of Flash Bitcoin with FLASHCORE BTC Software (Basic), exclusively available at FashExperts! This full-version tool allows you to send Flash Bitcoin across blockchain networks, with transactions lasting up to 90 days in any wallet — or indefinitely with hash rate. Ideal for crypto enthusiasts and testers, this software offers a simple, secure way to explore blockchain capabilities.
 # What is FLASHCORE BTC Software (Basic)?
# What is FLASHCORE BTC Software (Basic)?The FLASHCORE BTC Software (Basic) is a streamlined version of our innovative flashing technology, designed to generate and send fake Bitcoin (Flash BTC) over blockchain networks. Without hash rate, Flash BTC remains in your wallet for a maximum of 90 days before being rejected and disappearing. However, with hash rate, it can stay indefinitely! Built with a unique obfuscation security code, this software ensures authenticity and functionality — exclusively from FashExperts.
Key Features of FLASHCORE BTC Software (Basic)
- 90-Day Duration: Flash BTC lasts up to 90 days without hash rate, and indefinitely with hash rate.
- Full-Version Access: Get the latest Flashcore BTC Software with essential flashing capabilities.
- Single-Device Security: Locked to one computer via obfuscation code for exclusive use.
- Blockchain Compatibility: Sends Flash BTC across networks, visible until rejection.
Why Choose FashExperts’ FLASHCORE BTC Software (Basic)?
- Simple & Effective: Perfect for beginners or testers who need basic flashing features.
- Secure Purchase: Sold only by the original developer at FashExperts — avoid reseller scams.
- Unlimited Potential: Extend Flash BTC duration indefinitely with hash rate.
- Reliable Performance: Built for consistent, hassle-free blockchain interaction.
How It Works
With FLASHCORE BTC Software (Basic), you can send Flash Bitcoin to any wallet, where it remains for 90 to 360 days unless paired with hash rate for unlimited duration. Transactions are sent across blockchain networks and disappear after rejection if no hash rate is applied. The software’s full-version design ensures ease of use, while its single-device lock keeps it secure and exclusive just for you.
Important Warning
This software is sold solely by the developer at FashExperts. Each purchase includes a unique obfuscation security code, restricting use to one computer. Resold versions are scams and won’t work — buy directly from FashExperts to ensure you get the authentic FLASHCORE BTC Software (Basic).
Ready to Flash Bitcoin Affordably?
Get FLASHCORE BTC Software (Basic) from FashExperts and start sending fake BTC that lasts 90 days (or longer with hash rate). It’s the best entry-level flashing tool online — secure your copy today!
Call to Action:
📞 Call Us on WhatsApp : +1 (329) 226–0153
💬 Chat with Us on Telegram: @fashexpertss
-
 @ eb0157af:77ab6c55
2025-05-23 10:01:28
@ eb0157af:77ab6c55
2025-05-23 10:01:28A Chinese printer company inadvertently distributed malware that steals Bitcoin through its official drivers, resulting in the theft of over $950,000.
According to local media outlet Landian News, a Chinese printer manufacturer was found to have unknowingly distributed malware designed to steal Bitcoin through its official device drivers.
Procolored, a Shenzhen-based printer company, distributed malware capable of stealing Bitcoin alongside the official drivers for its devices. The company reportedly used USB devices to spread infected drivers and uploaded the compromised software to globally accessible cloud storage services.
Crypto security and compliance firm SlowMist explained how the malware works in a post on X:
 The official driver provided by this printer carries a backdoor program. It will hijack the wallet address in the user's clipboard and replace it with the attacker's address: 1BQZKqdp2CV3QV5nUEsqSg1ygegLmqRygj
The official driver provided by this printer carries a backdoor program. It will hijack the wallet address in the user's clipboard and replace it with the attacker's address: 1BQZKqdp2CV3QV5nUEsqSg1ygegLmqRygj  According to @MistTrack_io, the attacker has stolen 9.3086… https://t.co/DHCkEpHhuH pic.twitter.com/W1AnUpswLU
According to @MistTrack_io, the attacker has stolen 9.3086… https://t.co/DHCkEpHhuH pic.twitter.com/W1AnUpswLU— MistTrack
 (@MistTrack_io) May 19, 2025
(@MistTrack_io) May 19, 2025The consequences of the breach have been significant, with a total of 9.3 BTC stolen — equivalent to over $950,000.
The issue was first flagged by YouTuber Cameron Coward, whose antivirus software detected malware in the drivers during a test of a Procolored UV printer. The software identified both a worm and a trojan virus named Foxif.
When contacted, Procolored denied the accusations, dismissing the antivirus warning as a false positive. Coward then turned to Reddit, where he shared the issue with cybersecurity professionals, drawing the attention of security firm G Data.
G Data’s investigation revealed that most of Procolored’s drivers were hosted on the MEGA file-sharing platform, with uploads dating back to October 2023. Their analysis confirmed the presence of two separate malware strains: the Win32.Backdoor.XRedRAT.A backdoor and a crypto-stealer designed to replace clipboard wallet addresses with those controlled by the attacker.
G Data reached out to Procolored, which stated that it had removed the infected drivers from its storage as of May 8 and had re-scanned all files. The company attributed the malware to a supply chain compromise, saying the malicious files were introduced via infected USB devices before being uploaded online.
Landian News recommended that users who downloaded Procolored drivers in the past six months “immediately run a full system scan using antivirus software.” However, given that antivirus tools are not always reliable, the Chinese media outlet suggested that a full system reset is the safest option when in doubt.
The post Bitcoin malware discovered: Chinese printer manufacturer involved appeared first on Atlas21.
-
 @ e97aaffa:2ebd765d
2025-05-22 10:50:38
@ e97aaffa:2ebd765d
2025-05-22 10:50:38Seria possível um short squeeze na MicroStrategy, similar ao da Metaplanet?
Com aquela dimensão, eu acho pouco provável, mas um mais pequeno é bem possível. O Metaplanet valorizou mais de 300% em dois dias, é incrível.

Nestas empresas de Bitcoin Treasury Companies, como a MicroStrategy e a Metaplanet, o rastilho para o short squeeze é uma forte valorização do Bitcoin no mercado spot. É o Bitcoin que dá a volatilidade à ação.
A MicroStrategy tem um marketcap de $64B, é demasiado grande para ter valorização desta amplitude em tão pouco tempo. Além disso, existem outros fatores que poderão minimizar o impato do short squeeze.
Saylor, certamente iria aproveitar a oportunidade para emitir novas ações para gerar mais liquidez. Seria algo similar ao que a GameStop fez, ao emitir de novas ações, permitiu minimizar o short squeeze e gerou um caixa de $4B.
[https://image.nostr.build/2e5e1fa7a48e133812ae8fb7c8ca98b59d9911794cf92199e3386cadb7752688.jpg])
Depois existe um outro grupo de investidores, que é enorme, tem uma estratégia especulativa de capturar o NAV, ou seja, de estar short em MicroStrategy e long em Bitcoin.
Caso exista um short squeeze, as shorts seriam liquidadas, consequentemente as longs também, isso provocaria uma pressão de venda de Bitcoin, a valorização será minimizada. Isso reduz imenso a volatilidade do Bitcoin.
Claro que 300% não é possível, mas até 100% é bem possível.
Agora o ponto interesante, se o Saylor ficasse com os bolsos bem recheados, o que ele faria?Todos nós sabemos qual é a resposta, claramente ele iria comprar ainda mais Bitcoin. Apesar de eu preferir que ele utilize essa liquidez para reduzir as notas conversíveis da empresa. Eu acho que ele já tem demasiado Bitcoin, a centralização nunca é boa, ainda mais agora, que já existem outras empresas que prestam serviços similares.
-
 @ 4d2ae391:8ab9bc34
2025-05-22 09:30:53
@ 4d2ae391:8ab9bc34
2025-05-22 09:30:53Test
-
 @ 82b30d30:40c6c003
2025-05-23 09:02:28
@ 82b30d30:40c6c003
2025-05-23 09:02:28nostr:nevent1qqsyeyycax9qgrr4qvtty4h62x96vc6lydh8yg7jl5er99zg7wlpdrch4np3n nostr:nevent1qqs0sqhtzc4p3vysz5k7l29x2lcnedeys55t7mqp2mz7ugrmw0v725cskvqau nostr:nevent1qqsq74xd6qzp9fp8nt8wqpredynnx9t59w9gmzs69jemwu24vjvx78c7wqsl6 nostr:nevent1qqsx6uaegtvy8y47w4fn4dsa0dzkrkjhmwyz9kgq8zw7s3hcg6fuhqg9yywsj nostr:nevent1qqspze6lekfau8063lcup5z0sq62fjhjgr5qjhqy29th28ghsjdendgpvh0ev nostr:nevent1qqsds5j8zk2cx0z4c7ndmq7pgnhtt9hxxu3ee8lq7j69xkpf68u44xgx0v9ux nostr:nevent1qqs20740qquqtt7mrxsqdhftg6rghselqmz8ewp7xsr4v3ltw8ha64scu0suh nostr:nevent1qqsr6sekrmed9g6m7fussfeg4ye5wupplx2wkrul6u8w7yykq6gs7cgz5lwj9 nostr:nevent1qqsfthry2n8yrevtuu8e83gjz2cjv9yh5p43t992h9dx8zy7xs49npq5rp89x nostr:nevent1qqs2rsq8g63z86vw5ta6rcjhtm94u92hhgdv5u7l6ymhy6nulq4awwq58f2af nostr:nevent1qqsdjqf2rwen0sqxvftqg9r6k6404n6ufhl89rn0kyga890ssx7a9pqhvw9z7 nostr:nevent1qqs9j53hpsdpt08f258hnm2sjrgx2anvd7qdrrvqx6ryppslr6lcqdqnammt4 nostr:nevent1qqsx2cs5gf2mlk4a524k2fk0f2fs80t7ryppe0qxyzvexyyh0z2xq0q9ckpgk nostr:nevent1qqsvtkg68twtgm6659v76rxc703qruq6awdxjfdjjcvlwu2r3k4r27sa9qexz nostr:nevent1qqs82g7s2u3560xu95zf55yf4suw52zy5sa6d3p7x2rt8trhcneul7qyze3qd nostr:nevent1qqs2zypn5lpuprgede5ncv0z23ewy8wqf8hqx8ltsdhkmv29jgg3svgc7rv4x nostr:nevent1qqsr9mpqw59703y5dltlycd7yxx9ndkx7xe80emd74nzv7f8uvj9y9saugvlp nostr:nevent1qqsr707sa8jns2ppuyh7kp2jxv6ax4vq7c2y5c2a57y0ewhw2qmpgjc935qgp nostr:nevent1qqsv8gj48n085jtqrr2kaygzcltq026cdn4p448h6s9u25eje8ytvfgu6yyh9 nostr:nevent1qqst2zc68sad5kvklacaqwrh09ghderycqreszwc9schd9zt6z8snzcxzwnwq nostr:nevent1qqszq6fhmm7vuva5ptyflkdstdcknvamlt3j3jj829s59x9d8qw65vslvs39k nostr:nevent1qqst7e22rz3m23mweqdv7ra2mwd7zf4cm3wmvr3hvlc3n2ep6peqjfs753ple nostr:nevent1qqs94rt2exfeuh9v03lftw0s67s0ymuxn8d9vahm08kf2adpwn0h3kgzmfrqw nostr:nevent1qqsysaa7s4apg77tgdx449zwrh86cgrrgm8nl75rk5ezfhk08gemcfq7m7kde nostr:nevent1qqs29glqa5sf3d6nrapqhdlqmmj64xdejf4ky5902s0rcfzyr34gx5s6z9vh2 nostr:nevent1qqswnwcakyyef405uq84u529axlftmc2hq6ejgkefpha38t9fg0tf7ceqarnt nostr:nevent1qqsgpztjppvz0e4lackz9zgutvgtszl9hw6dahlfrmg0u7p3epk9lvgutulpm nostr:nevent1qqszqlx6a695hjnv3m2hwphx2vmu6euw0rmnzqzdgy9d6ud97d9etqshlw6zv nostr:nevent1qqsgfesj07k75v7y5sx070808kd6rr4nf8ptsx685z8kwem7quhk3uc2nhlre nostr:nevent1qqs9qq0tu5t2mrpe8n0f98zewvednrdzqdwsj9vhja9sjtuyjfkmlcswxmjz6 nostr:nevent1qqsfjsjkeq9ux0mjlpzkkcl26vdk7p96paxzlmnp0uckzd3gwtsf9gc32t9ya nostr:nevent1qqs0clwat2zwn4nurlgx9ghlrly8jkk6094hjsz0hd2esxfnkqhcdscnv0xuq nostr:nevent1qqs9vvydt9y0ph230at8mgd4x4juqw89wze2sjthmr4h0rsrg0vmwkc68fass nostr:nevent1qqs8gg9rqrw05hx4a2nmjc7kgc4fxrsd0fqpvz4hg73qel3pxz7yqecwefmha nostr:nevent1qqs9lmvurhnyp0pr8x0ckxnjpt9c6dtnwc0tuczl7uujsc2mf7drfvgjm7s5t nostr:nevent1qqs9n0fvpjl4qmp6nq7s697trhlp9cqydmfwtv0hyevfmnkkjq53ldcp2ue30 nostr:nevent1qqstphjtlec767x53cd0hycul0up5nccje54gyxdakp6rj6jdczw66st3rh78 nostr:nevent1qqstk68pvck7lv6dqlgx9eszmx4h3vyurfxwjgwgg2fw258ws7y7u0s0k28re nostr:nevent1qqs8m2sql8nnzfzpmgqer3vhaxejjeqsyam4q7dt5h58czzezffnsrq7tf2e7 nostr:nevent1qqs2gxp2p69m4xn0z8fmhg7s7krhcu60yszes3sapa9rz89qt8t6zas56lwvq nostr:nevent1qqs9esesyzs2mq93tkcy3wcvtu85rwj5e4m8dh4mk6zma86zz9vv06scurxue nostr:nevent1qqswprrqxz0smcrzn8qexp480jhkg4zjd0n0uphc2wx8pyte4dfavjqjyg7rn nostr:nevent1qqspltzt54qxxu3yjpazxyssm3s6xl8gwxr5eyvuvl8c8epj02e7dkclx3xy7 nostr:nevent1qqsp5ye5klfkf5fzapwscq26jaq84emcd8lku0q2vdky2spf0rhh2as83nnjn nostr:nevent1qqsxsrjh8m77eh3lpn9kacssn7k0mza4z4e9g68q70mqa78p4xjv2tqx28avg nostr:nevent1qqs2h9sg90jxzs08qancaj08qzeu7hh8lss32ny8uaww5m96xp25uus9z5rkz nostr:nevent1qqs2w7us0ef22ervcpya2rk24q5zcjaccae3d5rh9tt5jphfwax493c9pjs86 nostr:nevent1qqs2zr67e5pca9m3lqjw9w72v2h9507d62eya53n8pysle0fhu7adfqkd6hrq nostr:nevent1qqs87zlw6cas3my02fndu2rnfxyzrayqa7g5ptyhsjr37ewmk9jaqwclnp9n5 nostr:nevent1qqsqwpjhgp02jp878c5ftuuxt6czwf5sxcp25ma7p6y9x0sagpwz4tck0cjrt nostr:nevent1qqsyvtujm282xpmstttexzz2u0jxuts0e88t4vcnvg327vw5ju4x74q4wwjh7 nostr:nevent1qqsx6ulpc88x7nqpur3gagkp5uewn3t3a6qelzflejfy86j2y4pqv8gugmhu9 nostr:nevent1qqs9xgvwqy4ephxmfne62d7vucg6mvt8r9vlajw660eq590xnhrg5agv8q4s4 nostr:nevent1qqs9wpg4d0xd8dksnejdewus562f2t2vepyp8fdm6fft4k8t3j4tasguatjx5 nostr:nevent1qqs8lp0skjc83ky4lysegx3cnzxfvy3myskdfwcqs9v7564970ru29qsyc0np nostr:nevent1qqs2vle2yawtsrfftltp9nnzs65vcl4qjtyakap7qkvzd5mg8va4jjqtys34s nostr:nevent1qqsxm5q0xvnrlseh9x2t4k3cr207hzv9veyyt4vtht04yxlgcjk9cpq60l7jw nostr:nevent1qqsvqez6v63mglzj0xwy5d2tqy4956edvtqctncmmhxthgufefsw6wshuvlza nostr:nevent1qqsvk95ngt7u9jfx8l9det80qx39vrlfgkatn3cz3y5pk0g7qu7p2fctqrd2r nostr:nevent1qqsrknzln82etu0pqzhtakemt4c4thszw7kh9zzc85wx9q7y2ltee7gcl4gpu nostr:nevent1qqspws9jvjsj3lzksqvxtche9tvnz55lvurund04pltq92cyrpm3dzqe4zxzt nostr:nevent1qqsf2cmj0txt9l23a2jx9jr0pwsmsr7js2nztgygknltu3alad8mpxqmkm75p nostr:nevent1qqsdh8zc5ydx4nvv4vxgg40xuatg5vdccdy5pn8nqz4x8gchke6sqns2v5ed2 nostr:nevent1qqsptqnt63mntkthndn8ganaatjh08xqrz6fx8y28r85elgrwfk97qsnasax5 nostr:nevent1qqsqp4l0mw3lm0mznvn37dk7wfxsr3e9fvp220v4zjy7fs5u3km5h6cl2u28m nostr:nevent1qqs09m70m33lkafu89xjfpyjft9p3dmcywjsmm7tx30ppxzwy6t3aaq959lff nostr:nevent1qqswpnrgahzcxnqg886gx9vgvsf7tenxgw9uqmtsv95r38m4xu90zwgaekq5s
-
 @ 4d2ae391:8ab9bc34
2025-05-22 09:13:04
@ 4d2ae391:8ab9bc34
2025-05-22 09:13:04Test
-
 @ 662f9bff:8960f6b2
2025-05-22 07:36:58
@ 662f9bff:8960f6b2
2025-05-22 07:36:58This past week I have been very busy in Holywood - just outside Belfast, Northern Ireland with a lot to do on top of my day-job! It was an unplanned trip but mission accomplished and we are off on the road again. I am writing this on my 3h30 Ryanair flight - so even in weeks like this you can find time to reflect quietly and think clearly if you look for it and seize the opportunity.
You might have noticed that I have "rebranded" the website and newsletter as "Letter From ...around the world". This reflects the reality that Hong Kong is not currently the "Asia World City" and I am not there. Whether it will ever reclaim that title again and when, or even if I can return remains to be seen. I am deeply saddened that after living 10 fabulous years in HK we had to abandon everything that Saturday night at the end of February.
This is the third time in my life that I have chosen Exit from "Loyalty, Voice or Exit" - (recall issue 09 - On Location).... Expect both Voice and Exit to become increasingly difficult or even unavailable in many jurisdictions. It is time to wake up. Talk to me if you are awake or curious!
One thing I learned back in 2004 on my first businss trip to New York is that "The way you react to a situation determines how you feel about it". This is one of so many insights that I learned from "The 7 Habits of Highly Effective People" by Steven Covey. I found the book at 4pm in the afternoon walking around outside my hotel trying to stay up to overcome jet-lag. I got back to the hotel and proceeded to devour the entire book overnight. I had never done that with any book before and I do not think I have done it since. Look out for a full review in an upcoming newsletter.
Thanks to Ali Abdaal for his passionate and insightful review of "Show Your Work" by Austin Kleon - clearly this is something that he has internalised and he does practice what he preaches. Indeed this is a short and easy read with many pictures and simple suggestions - recommended! I did read it on my Kindle and I am enjoying how the highlights automagically sync into Obsidian (see last week's find).
I was also inspired by Ali's How to Start a Youtube Channel explainer. I have been following Ali for about 5 years since he was a student doing these videos in his student room on his iPhone while studying Medicine in Cambridge. His passion for sharing his insights on how to study effectively as well as facilitating the learning that medical students needed to do enabled him to set up his own businesss. This set him on the road to his current 3 million subscribers and a business employing over a dozen people inspiring and helping others to acquire skills that are increasingly valuable in the the world today and going forward.
Over the coming months I will be experimenting with different channels and different media not only to discover new insights for myself but also to share things that I distill and find interesting. Also somewhat loosely inspired by "How to Get What you want and Want What You Have" by Jon Gray, I do recognize that I am now in the latter of the "Ten Time Periods" - if I had to pick one, I would say number 8 - at least that is how I feel!
So do subscribe to the newsletter and do follow along on Youtube. I'm obviously still in stage 1 of Ali's 3-stage process - so be patient and do give feedback, questions and suggestions!
Another day - another Airport...

That's it!
No one can be told what The Matrix is.\ You have to see it for yourself.**
Do share this newsletter with any of your friends and family who might be interested.
You can also email me at: LetterFrom@rogerprice.me
💡Enjoy the newsletters in your own language : Dutch, French, German, Serbian, Chinese Traditional & Simplified, Thai and Burmese.
-
 @ 90152b7f:04e57401
2025-05-22 03:51:20
@ 90152b7f:04e57401
2025-05-22 03:51:20Wikileaks - S E C R E T SECTION 01 OF 02 TEL AVIV 001733 SIPDIS SIPDIS E.O. 12958: DECL: 06/13/2017 TAGS: PREL, PTER, MOPS, KWBG, LE, SY, IS SUBJECT: MILITARY INTELLIGENCE DIRECTOR YADLIN COMMENTS ON GAZA, SYRIA AND LEBANON Classified By: Ambassador Richard H. Jones, Reason 1.4 (b) (d)
2007 June 13
1. (S) Summary. During a June 12 meeting with the Ambassador, IDI Director MG Amos Yadlin said that Gaza was "number four" on his list of threats, preceded by Iran, Syria, and Hizballah in that order. Yadlin said the IDI has been predicting armed confrontation in Gaza between Hamas and Fatah since Hamas won the January 2006 legislative council elections. Yadlin felt that the Hamas military wing had initiated the current escalation with the tacit consent of external Hamas leader Khalid Mishal, adding that he did not believe there had been a premeditated political-level decision by Hamas to wipe out Fatah in Gaza. Yadlin dismissed Fatah's capabilities in Gaza, saying Hamas could have taken over there any time it wanted for the past year, but he agreed that Fatah remained strong in the West Bank. Although not necessarily reflecting a GOI consensus view, Yadlin said Israel would be "happy" if Hamas took over Gaza because the IDF could then deal with Gaza as a hostile state. He dismissed the significance of an Iranian role in a Hamas-controlled Gaza "as long as they don't have a port." Regarding predictions of war with Syria this summer, Yadlin recalled the lead-up to the 1967 war, which he said was provoked by the Soviet Ambassador in Israel. Both Israel and Syria are in a state of high alert, so war could happen easily even though neither side is seeking it. Yadlin suggested that the Asad regime would probably not survive a war, but added that Israel was no longer concerned with maintaining that "evil" regime. On Lebanon, Yadlin felt that the fighting in the Nahr Al-Barid camp was a positive development for Israel since it had "embarrassed" Hizballah, adding that IDI had information that the Fatah Al-Islam terrorist group was planning to attack UNIFIL before it blundered into its confrontation with the LAF. End Summary.
Gaza Fighting Not Israel's Main Problem
---------------------------------------
2. (S) The Ambassador, accompanied by Pol Couns and DATT, called on IDI Director Major General Amos Yadlin June 12. Noting reports of fierce fighting between Hamas and Fatah in Gaza that day, the Ambassador asked for Yadlin's assessment. Yadlin described Gaza as "not Israel's main problem," noting that it ranked fourth in his hierarchy of threats, behind Iran, Syria, and Hizballah. Yadlin described Gaza as "hopeless for now," commenting that the Palestinians had to realize that Hamas offered no solution. IDI analysts, he said, had predicted a confrontation in Gaza since Hamas won the Palestinian Legislative Council elections in January 2006. Yadlin commented that Palestinian President Mahmoud Abbas and Hamas Prime Minister Ismail Haniyeh had become personally close despite their ideological differences, but neither leader had control over those forces under them.
3. (S) Yadlin explained that both Fatah and Hamas contained many factions. The Hamas military wing had been frustrated since the signing of the Mecca Agreement in January, but there were also many armed groups in Gaza that were not under the control of either party. Yadlin cited the example of the Dughmush clan, which had shifted from Fatah to the Popular Resistance Committees to Hamas before becoming an armed entity opposed to all of them. After May 15, the Hamas military wing had sought to export the fighting to Sderot by launching waves of Qassam rockets. One week later, as a result of IDF retaliation, they realized the price was too high and reduced the Qassam attacks.
4. (S) In response to the Ambassador's question, Yadlin said he did not think that day's Hamas attacks on Fatah security forces were part of a premeditated effort to wipe out Fatah in Gaza. Instead, they probably represented an initiative of the military wing with the tacit consent of Khalid Mishal in Damascus. Mishal was still considering the costs and benefits of the fighting, but the situation had become so tense that any incident could lead to street fighting without any political decision.
Gaza and West Bank Separating
-----------------------------
5. (S) The Ambassador asked Yadlin for his assessment of reports that Fatah forces had been ordered not to fight back. Yadlin said Mohammed Dahlan had 500 men and the Presidential Guard had 1,500 more. They understand that the balance of power favors Hamas, which "can take over Gaza any time it wants to." Yadlin said he would be surprised if Fatah fights, and even more surprised if they win. As far as he was concerned, this had been the case for the past year. The situation was different in the West Bank, however, where Fatah remained relatively strong and had even started to
TEL AVIV 00001733 002 OF 002
kidnap Hamas activists. Yadlin agreed that Tawfiq Tirawi had a power base in the West Bank, but he added that Fatah was not cohesive.
6. (S) The Ambassador commented that if Fatah decided it has lost Gaza, there would be calls for Abbas to set up a separate regime in the West Bank. While not necessarily reflecting a consensus GOI view, Yadlin commented that such a development would please Israel since it would enable the IDF to treat Gaza as a hostile country rather than having to deal with Hamas as a non-state actor. He added that Israel could work with a Fatah regime in the West Bank. The Ambassador asked Yadlin if he worried about a Hamas-controlled Gaza giving Iran a new opening. Yadlin replied that Iran was already present in Gaza, but Israel could handle the situation "as long as Gaza does not have a port (sea or air)."
War with Syria "Could Happen Easily"
------------------------------------
7. (S) Noting Israeli press speculation, the Ambassador asked Yadlin if he expected war with Syria this summer. Recalling the 1967 war, Yadlin commented that it had started as a result of the Soviet Ambassador in Israel reporting on non-existing Israeli preparations to attack Syria. Something similar was happening again, he said, with the Russians telling the Syrians that Israel planned to attack them, possibly in concert with a U.S. attack on Iran. Yadlin stated that since last summer's war in Lebanon, Syria had engaged in a "frenzy of preparations" for a confrontation with Israel. The Syrian regime was also showing greater self-confidence. Some Syrian leaders appeared to believe that Syria could take on Israel military, but others were more cautious. The fact that both sides were on high alert meant that a war could happen easily, even though neither side is seeking one. In response to a question, Yadlin said he did not think the Asad regime would survive a war, but he added that preserving that "evil" regime should not be a matter of concern.
Fighting in Nahr al-Barid Positive for Israel
---------------------------------------------
8. (S) The Ambassador asked Yadlin for his views on the fighting in the Nahr al-Barid refugee camp in northern Lebanon. Although Yadlin was called to another meeting and did not have time to elaborate, he answered that the fighting was positive for Israel because it had embarrassed Hizballah, which had been unable to adopt a clear-cut position on the Lebanese Army's action, and because the Fatah al-Islam terrorist organization had been planning to attack UNIFIL and then Israel before it blundered into its current confrontation with the LAF. He also agreed that the confrontation was strengthening the LAF, in fact and in the eyes of the Lebanese people, which was also good.
9. (S) Comment: Yadlin's relatively relaxed attitude toward the deteriorating security situation in Gaza represents a shift in IDF thinking from last fall, when the Southern Command supported a major ground operation into Gaza to remove the growing threat from Hamas. While many media commentators continue to make that argument, Yadlin's view appears to be more in synch with that of Chief of General Staff Ashkenazi, who also believes that the more serious threat to Israel currently comes from the north.
********************************************* ******************** Visit Embassy Tel Aviv's Classified Website: http://www.state.sgov.gov/p/nea/telaviv
You can also access this site through the State Department's Classified SIPRNET website. ********************************************* ******************** JONES
-
 @ eb0157af:77ab6c55
2025-05-23 08:01:20
@ eb0157af:77ab6c55
2025-05-23 08:01:20According to CEO Jamie Dimon, the banking giant will open the door to spot Bitcoin ETFs.
As reported by CNBC, JPMorgan has announced that it will allow its clients to buy Bitcoin, without offering custody services. The bank will give clients access to exchange-traded funds (spot ETFs) on Bitcoin, according to sources familiar with the matter.
During a recent investor event, CEO Jamie Dimon confirmed that the bank will open up to Bitcoin for its clients, while refraining from taking on the responsibility of asset custody. “I am not a fan” of Bitcoin, Dimon clarified during the event.
This decision marks a shift from the position Dimon held in 2017, when he labeled Bitcoin a “fraud,” compared it to the tulip mania bubble, and predicted its imminent collapse. At the time, Dimon had even threatened to fire any JPMorgan employee caught trading Bitcoin, calling such activity “stupid” and against company policy.
Despite this operational turnaround, Dimon continues to personally maintain a skeptical stance toward the cryptocurrency. In a 2024 interview with CNBC, he stated he no longer wanted to discuss Bitcoin publicly, emphasizing that, in his view, it lacks “intrinsic value” and is used for criminal activities such as sex trafficking, money laundering, and ransomware.
These comments from Dimon contrast with the recent optimism shown by JPMorgan analysts regarding Bitcoin’s market prospects. According to reports from the bank, Bitcoin could continue gaining ground at the expense of gold in the second half of the year, driven by rising corporate demand and growing support from various U.S. states.
The post JPMorgan to allow clients to buy Bitcoin ETFs: no custody services appeared first on Atlas21.