-
 @ 90c656ff:9383fd4e
2025-05-17 10:26:42
@ 90c656ff:9383fd4e
2025-05-17 10:26:42Millions of people around the world still lack access to basic banking services, whether due to lack of infrastructure, bureaucratic requirements, or economic instability in their countries. Bitcoin emerges as an innovative solution to this problem, allowing anyone with internet access to have control over their money without relying on banks or governments. By offering an open and accessible financial system, Bitcoin becomes a powerful tool for global financial inclusion.
- The problem of financial exclusion
In many developing countries, a large portion of the population does not have a bank account. This can happen for several reasons, such as:
01 - Lack of access to banks: Many communities, especially in rural areas, do not have nearby financial institutions.
02 - Bureaucratic requirements: Some banks require specific documentation or a credit history that many people cannot provide.
03 - High costs: Banking fees can be prohibitive for those with low incomes.
04 - Economic and political instability: In countries with high inflation or unstable governments, banks may not be a safe option for storing money.
These challenges leave millions of people on the margins of the financial system, unable to save, invest, or carry out transactions efficiently.
- Bitcoin as an alternative
Bitcoin addresses many of the issues of financial exclusion by offering an accessible and decentralized system. With Bitcoin, anyone with a mobile phone and internet access can store and transfer money without needing a bank. Key advantages include:
01 - Global accessibility: Bitcoin can be used anywhere in the world, regardless of the user's location.
02 - No intermediaries: Unlike banks that impose fees and rules, Bitcoin allows direct transactions between people.
03 - Low-cost international transfers: Sending money to another country can be expensive and slow with traditional methods, while Bitcoin offers a faster and more affordable alternative.
04 - Protection against inflation: In countries with unstable currencies, Bitcoin can be used as a store of value, protecting the population’s purchasing power.
- Use cases in financial inclusion
Bitcoin is already being used to promote financial inclusion in various parts of the world. Some examples include:
01 - Africa and Latin America: In countries like Nigeria, Venezuela, and Argentina, where inflation is high and access to U.S. dollars is limited, many people use Bitcoin to preserve their money and make international transactions.
02 - International remittances: Workers sending money to their families abroad avoid the high fees of traditional transfer companies by using Bitcoin.
03 - Digital microeconomy: Small merchants and freelancers without access to bank accounts can receive payments in Bitcoin directly and securely.
- Challenges to financial inclusion with Bitcoin
Despite its advantages, Bitcoin adoption as a tool for financial inclusion still faces some challenges, such as:
01 - Internet access: Many impoverished regions still lack adequate digital infrastructure.
02 - Financial education: Greater knowledge of the technology and best security practices is needed for broader adoption.
03 - Price volatility: Value fluctuations can make Bitcoin difficult to use for everyday expenses, especially in countries where people live on unstable incomes.
In summary, Bitcoin offers a viable solution for millions of people excluded from the traditional financial system. By providing global access, low-cost transactions, and protection from inflation, it becomes a powerful instrument for promoting financial inclusion. However, for its full potential to be realized, it is essential to invest in digital education and expand technological infrastructure, enabling more people to achieve financial autonomy through Bitcoin.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ c1831fbe:de4b39bf
2025-05-17 09:57:04
@ c1831fbe:de4b39bf
2025-05-17 09:57:04What follows is my best effort to recall the details of an arguably supernatural encounter I experienced almost sixty years ago. I've told this story many times before, and while my recollection may not be perfect in every detail, my account is real and substantively factual.
It was early one long ago morning, in that twilit between-time shortly before dawn. As I dangled precariously in a quasi-aware state, hovering on the knife edge between wakefulness and sleep, I was transported in a dream to another place and time. Was it the Mediterranean coast? Perhaps ancient Greece?
In my mind's eye, I found myself climbing a rather steep, rocky hillside overlooking a sparkling bright blue sea. Ahead of me, and slightly higher, was what appeared to be a young shepherd boy, leading me ever higher up the hill.
As we wove our way upward,
skirting rocky outcroppings and zig-zagging because of the steepness of the slope, I heard the boy chanting:
"Ata, Ata, Archontos, Ata, Ata, Echousi, Ata, Ata, Archousi"
He kept repeating the mantra, over and over:
"Ata, Ata, Archontos, Ata, Ata, Echousi, Ata, Ata, Archousi"
\~ \~ \~
"Ata, Ata, Archontos, Ata, Ata, Echousi, Ata, Ata, Archousi"
I listened for a few cycles, and then took up the chant myself. After several attempts, when at last I got it right, the shepherd boy turned, looking back at me and smiling broadly to signal that I had finally mastered the cadence and the words.
Then I awoke.
Because my dream had been so vivid and unusual, I immediately found a pencil and paper to write down the chant phonetically before I could forget it.
A few days passed.
Life was busy. Then I remembered my friend in grad school, studying biblical Greek. That weekend, I went and hung out with him while he worked his night job at the college heating plant. Between his rounds inspecting and managing the steam boilers keeping students from freezing to death in the Arctic Midwest winter, I told him about my strange dream.
Pulling out an exhaustive Greek lexicon, one by one, my knowledgeable friend looked up the words from my dream, interpreting each according to its verb conjugation, tense, and mood.
"Ata, Ata" had no discernible meaning; we soon concluded that it was probably just meaningless vocables, added to give the chant rhythm and substance. My friend moved on to the first recognizable word of the chant...
"Archontos" - "They are ruled."
OK, so far, so good. He checked the next word:
"Echousi" - "They shed blood."
Hmmmm... This chant is beginning to appear to be more than random sounds.
"Archousi" - "They rule."
At this point, I almost fell out of my chair in shock. Far from being a meaningless chant, this cycle—repeating again and again—is the seemingly never-ending story of the entirety of human history...
"They Are Ruled, They Shed Blood, They Rule."
\~ \~ \~
"They Are Ruled, They Shed Blood, They Rule."
This concise mantra perfectly captures the endlessly repeating cycle of oppression, revolt, and revolution that always leaves us with a fresh set of oppressors all too ready to replace the last.
Who will rescue us?
Who will redeem us from this endless tedious cycle into which we have been born?
A long lifetime of study and reflection has persuaded me that this deadly cycle can and ultimately will be broken. If we follow the teachings of Jesus; if we love one another and live together in voluntary, local societies, serving each other; I am persuaded that we can break free of this desperately destructive cycle of endlessly seeking to dominate one another. It's past time for us to enter into a mutually beneficial life in the Kingdom of our Creator-God Jesus, the most authentically benevolent King the universe has ever known.
stories #politics #Christianity #supernatural #strange
-
 @ 5edbd885:5fbc291e
2025-05-17 09:54:39
@ 5edbd885:5fbc291e
2025-05-17 09:54:39Because Bitcoin operates outside traditional financial and political systems, engaging with it can create cognitive dissonance.
This uneasy tension is felt in the space between a lifetime of systemic conditioning and the reality of a protocol that functions beyond anything we have ever known.
Bitcoin challenges deeply ingrained assumptions about what money is, who should control it, and how trust is established in society.
Many initially reject it because Bitcoin breaks the mental models we’ve relied on for understanding value, authority, and trust.
It’s not just adopting a new system; it’s detaching from the old one and any -ism we may personally identify with.
Before we dive in I would like to make an important note about our current system.
Modern Fiat is Not Capitalism
Capitalism is an economic system in which private individuals or businesses own and control the means of production, distribution, and exchange of goods and services, rather than the state.
The main features of this system are limited government intervention, a free market economy, and competition.
While we may believe we live in a capitalistic society, reality is very different:
-
Governments Intervention: Governments intervene in free markets primarily through monetary expansion (money printing) and capital controls.
-
Inflation and Redistribution: Printing increases the money supply, causing inflation that erodes purchasing power unevenly. Those who receive new money first gain at the expense of later recipients. Capital controls restrict market flows, distorting asset and currency prices.
-
Cantillon Effect and Concentration: These mechanisms concentrate wealth and economic power among government insiders and favored corporations, who gain preferential access to resources. This leads to growing government influence and corporate monopolies.
-
Systemic Distortions: Such interventions stifle innovation, reduce market competition, and undermine price signals essential to free market functioning.
-
Therefore: Our modern fiat monetary system is not free market capitalism.
To quote Jeff Booth, from first principles:
> “In a free market, prices fall to the marginal cost of production; if they are not falling, we do not live in a free market. Communism and capitalism are the same system under manipulated money.”
Bitcoin is the first opportunity for humanity to experience a true free market where prices fall—a reality beyond fiat altogether.
Let’s explore how Bitcoin differs from fiat-based systems and economic theories.
Bitcoin vs. Major -isms
| Feature | Capitalism | Communism | Libertarianism | Bitcoin | | ------------------------- | ------------------------------------ | ----------------------------------------- | ------------------------------------ | ------------------------------------------------- | | Ownership Model | Private, profit-driven | Collective, state-owned | Private, voluntary exchange | Individual, self-sovereign | | Control of Money | Central banks & private institutions | State-controlled | Privatized or gold-backed | Decentralized, algorithmic issuance | | Value Flow | Favors asset owners | Centralized and controlled redistribution | Market-driven | Distributed to all network participants | | Ideological Basis | Market efficiency, competition | Class struggle, equality | Individual freedom, non-intervention | Neutral protocol, transparency, free market | | Governance Structure | Market and government interplay | Centralized planning | Minimal state | Consensus among decentralized nodes | | Inflation Policy | Targeted via central banking | Controlled by state | Opposed to fiat inflation | Hard-capped supply: 21 million BTC | | Censorship Resistance | Low to moderate (depends on regime) | Low | Medium, still requires trust | Very high—no central chokepoint | | Accessibility | Varies by class and location | Controlled by state allocation | Varies by market access | Global, permissionless | | Moral Foundation | Efficiency and growth | Equity and solidarity | Autonomy and property rights | Mathematical integrity, sovereignty, transparency |
Bitcoin is not an -ism or a fiat system.
I don't see it as a way to make more fiat paper money either.
It’s a system outside the system that breaks all of our previous mental models.
A truly interdependent reality where the creativity, productivity, gifts, talents, and abilities of one serves all.
Sovereign individuals in service of the collective and vice-versa.
The Difficulty Categorizing Free Thinkers
In different conversations, and while discussing Bitcoin with non-Bitcoiners, I’ve been asked if I am an anarchist, capitalist, communist, liberal, or a libertarian.
Since I don’t identify with any political leaning or traditional ideology, I was sincerely confused when this first started happening—but now I see why.
Bitcoiners are notoriously difficult to place into political categories because their convictions often cut across traditional ideological boundaries.
To the outside observer, this can appear contradictory: a Bitcoiner might criticize the Federal Reserve like a libertarian, value personal personal sovereignty like an anarchist, and believe in sound money like a gold-standard capitalist.
These labels, however, fail to capture the deeper thread—I believe our views are aligned with a protocol in service of humanity, and shaped by a shared belief in a system that values humans rather than fiat-based incentives.
Bitcoin challenges the default left/right binary and exposes just how much our frameworks are built around centralized systems, division, and control.
When those systems are removed—as they are in Bitcoin—any traditional world view falls apart, along with all the labels and polarization that come with it.
To some, this may be why Bitcoiners seem ‘radical’ or ‘religious,’ because we have stepped outside their frame of reality entirely.
This protocol is not a revolution in the name of an ideology—it’s a revolution in the absence of one known to modern history.
Unlearning the Past, Embracing the Now
What makes Bitcoin truly disruptive isn’t just its technology—it invites us to question assumptions we didn’t even know we were making.
I still catch myself trying to compare Bitcoin to a "known" sometimes in this ongoing process of unlearning.
I think part of this evolution is catching myself and remembering, we are at the forefront of a new reality.
Our individual choices and actions are shaping what the post-fiat world will look like.
While for some, this will feel empowering and exciting, for others, this shift can feel unsettling, even threatening, as it calls into question the stability of the familiar.
This is one of the reasons why I see Bitcoin as being the initiator of an individual and collective spiritual awakening.
I can only encourage you to embrace the change—be the change—a powerful manifestor ushering in a new paradigm ✨
-
-
 @ a4043831:3b64ac02
2025-05-17 09:03:00
@ a4043831:3b64ac02
2025-05-17 09:03:00Money is emotional. It’s not just numbers on a spreadsheet. It’s about peace of mind. Vacations. College. Retirement. And sometimes… It's about stress. Even the smartest families make money mistakes. Not because they don’t care. But because life is busy. Financial planning can feel overwhelming. And it’s easy to put it off until “later.” But the truth is: later turns into never.
Here are five common money missteps families make—and how to avoid them, starting today.
1. Spending Without a Plan
You’re out running errands. You grab a latte. Order takeout. Buy a couple things online. Nothing big. But by the end of the week? The bank account’s hurting. Sound familiar?
Many families spend without a clear plan. They don’t know exactly how much they earn, where their money is going, or what’s left for savings. It’s a recipe for stress.
How to avoid it: Start simple. Track your income. List your expenses. Identify where you can cut back. Use a budgeting app or just a notebook. The key is consistency. Build awareness around spending.
Working with a financial advisor makes this even easier. Passive Capital Management helps families create realistic, stress-free budgets that actually work.
2. Delaying Retirement Savings
Let’s be honest—retirement feels far away. Especially when you’re dealing with daycare, car payments, and rising grocery bills. But here’s the catch: the earlier you start, the less you have to save. Why? Two words: compound interest. The money you invest today earns interest. And then that interest earns interest. Over time, your money grows exponentially.
How to avoid it: Contribute to a 401(k), IRA, or both—right now. Even if it's just $50 a month. Got a workplace plan? Take full advantage of any employer match.
And don’t “set it and forget it.” Revisit your plan regularly with a trusted advisor. PCM’s retirement planning services help families build smart, flexible strategies tailored to their long-term goals.
3. Overusing Credit Cards
Swipe now, worry later. That’s the trap. Credit cards can be useful but dangerous when used for emotional or unplanned purchases. High-interest rates can turn a $100 dinner into a $300 debt headache.
How to avoid it: Use credit cards for planned expenses only. And pay off the balance in full each month. Avoid minimum payments—they just feed the debt cycle. If you’re already in credit card trouble, don’t panic.
Passive Capital Management works with families to create smart debt reduction plans while still saving for the future.
4. Buying Too Much House
Big house. Fancy kitchen. Bonus room. Sounds great, right? Until the mortgage, property taxes, repairs, insurance, utilities, and maintenance come crashing in. Many families make the mistake of maxing out their home budget. It feels like an investment—but in reality, it can squeeze your finances for decades.
How to avoid it: Buy what you need, not what impresses others. Be realistic about ongoing costs. And remember: your mortgage should never eat up your emergency savings or retirement goals. Before making a big move, talk to a financial expert.
PCM helps clients evaluate housing costs in the context of their full financial picture.
5. Skipping the Emergency Fund
Unexpected car repair? Out-of-pocket medical bill? Job loss? Life happens. And when it does, many families don’t have a cushion. They rely on credit cards or drain their retirement accounts just to stay afloat.
How to avoid it: Build an emergency fund with 3–6 months of essential expenses. Keep it in a separate, easy-access savings account. This fund is your safety net—don’t touch it unless it’s truly an emergency.
PCM includes emergency fund planning as a core part of every family’s financial plan. Because peace of mind isn’t optional—it’s essential.
Final Thoughts
Nobody gets it right 100% of the time. But small, consistent changes can transform your family’s financial future. The good news? You don’t have to do it alone. Passive Capital Management offers straightforward, judgment-free guidance to help families avoid costly mistakes and make confident money moves. Whether you need help building a budget, planning for retirement, or finally tackling your debt, PCM is ready to help.
Take the first step. Your future self will thank you. Talk to a PCM Advisor Today.
-
 @ e97aaffa:2ebd765d
2025-05-17 08:58:14
@ e97aaffa:2ebd765d
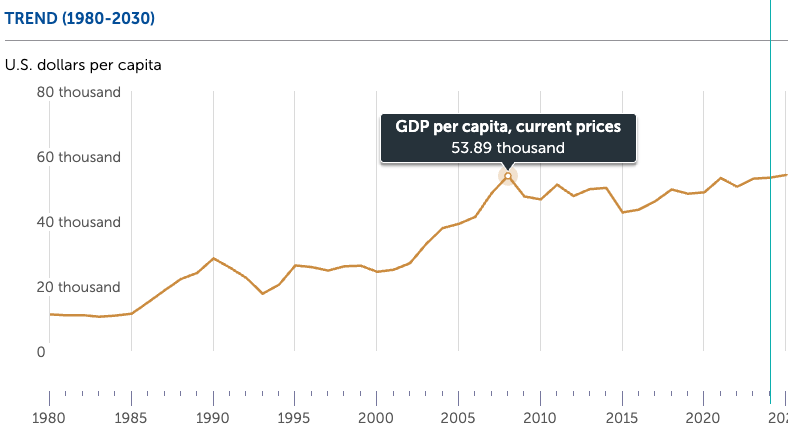
2025-05-17 08:58:14Quando tentamos simplificar/ilustrar algo que é extremamente complexo, pode resultar em algo distorcido. Apesar do resultado sair distorcido, continua a ser a melhor representação, temos é que ter em mente que essa distorção existe quando analisamos essa informação.
O maior exemplo, é o mapa mundi, quando transformamos uma esfera em algo plano, é natural que crie distorções, como quanto mais perto dos polos, os países são sobredimensionados em relação aos que estão mais perto da linha do Equador.
Esta infografia criada pelo Saylor é comumente utilizada, mas esta deve ser utilizada com moderação, porque a informação também está distorcida.
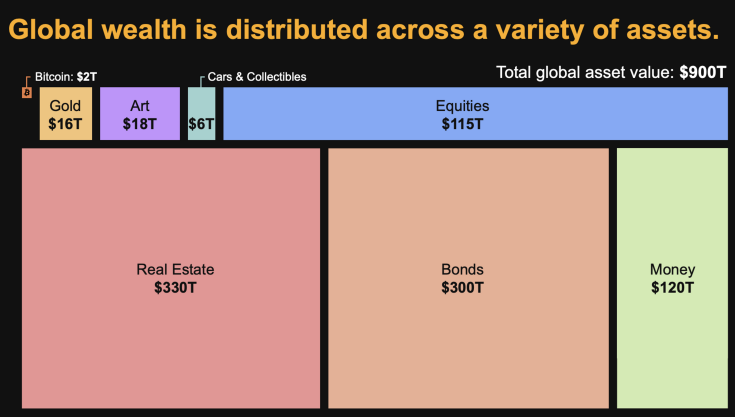
Assim, sempre que alguém utiliza estes dados para fazer análises, deve estar ciente que existem distorções. Primeiro, em alguns ativos os valores são impossíveis de calcular, são apenas estimativas. Já foram feitos vários estudos, e sempre com valores bastantes díspares.
Depois, esta infografia simplifica demasiado, não sendo visível a sobreposição de ativos, por exemplo, as empresas possuem outros ativos, isso significa, que não podemos fazer somas simples. Ou seja, se somarmos as Equities (115T) e os Bonds(300T) não resulta em $415 Triliões de riqueza, o real valor é inferior.
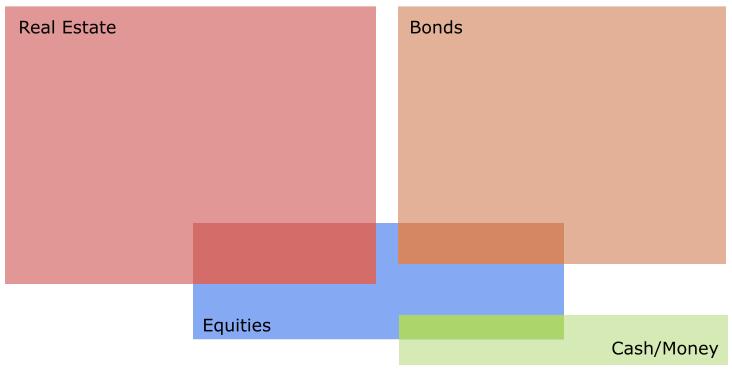
Vamos a dois bons exemplos:
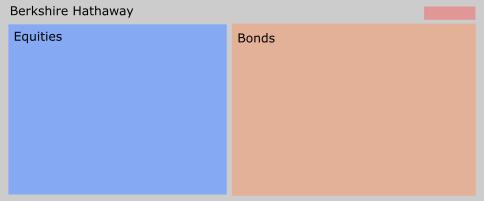
A Berkshire Hathaway, a empresa de Warren Buffett, que o seu atual core business é investir em outras empresas. Apesar de neste momento, ter uma enorme liquidez, está a aguardar pelo momento certo para voltar ao mercado.
A outra empresa é MicroStrategy, que gradualmente está-se a transformar num banco Bitcoin. O seu negócio inicial, começa a ser insignificante, para a sua atual dimensão, está a fazer um percurso muito similar à Berkshire Hathaway, enquanto a Berkshire Hathaway redirecionou o seu negócio para o investimento em ações, a MicroStrategy para o Bitcoin.
Um erro comum entre alguns bitcoiners quando fazem estimativas baseada nesta tabela, é acreditarem que o crescimento do valor do Bitcoin, vai resultar numa redução do valor das Equities. Isso não vai acontecer, porque as empresas também vão possuir Bitcoin na sua tesouraria, logo se o valor do bitcoin subir, as equities também o vão.
Onde o Bitcoin vai certamente impactar, é nas Bonds e no Real Estate.
Assim para concluir, esta infografia é interessante para fazer cálculos ou análises, mas não podemos esquecer que contém distorções.
-
 @ c913b8e3:8704332c
2025-05-17 08:31:43
@ c913b8e3:8704332c
2025-05-17 08:31:43Absurdities from Finland
Hydrogen, Railways, and Datacenters: Just an Armchair Economist Ranting (Expect Zero Value)
"Next year we'll have growth!" they promise. Again. And again. And again.
The "economists" who yell and preach about this are just state puppets. The track record: 17-18 years of zero growth.
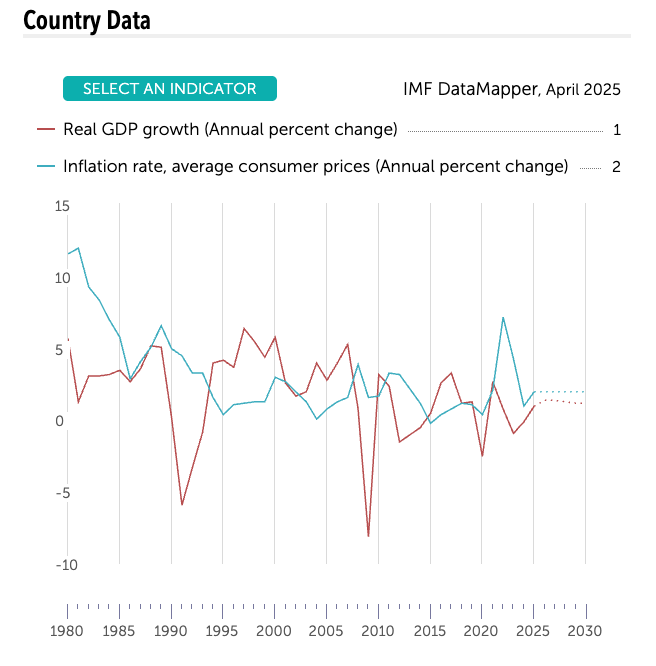
Finland, 1980-2025: Real GDP growth stagnant (red) while prices still bite (blue). After 2008 Red line - 17 years of “wait till next year.” — IMF DataMapper, April 2025
Why do the experts always get it wrong? Here in Finland, everybody is blinded by Keynesianism.
-
Low interest rates
-
High spending
Even those I once thought had "common sense" have become blind. They mistake subsidized sectors for "growth." So in love with the state, they ignore incentives, time preference, and basic economics.
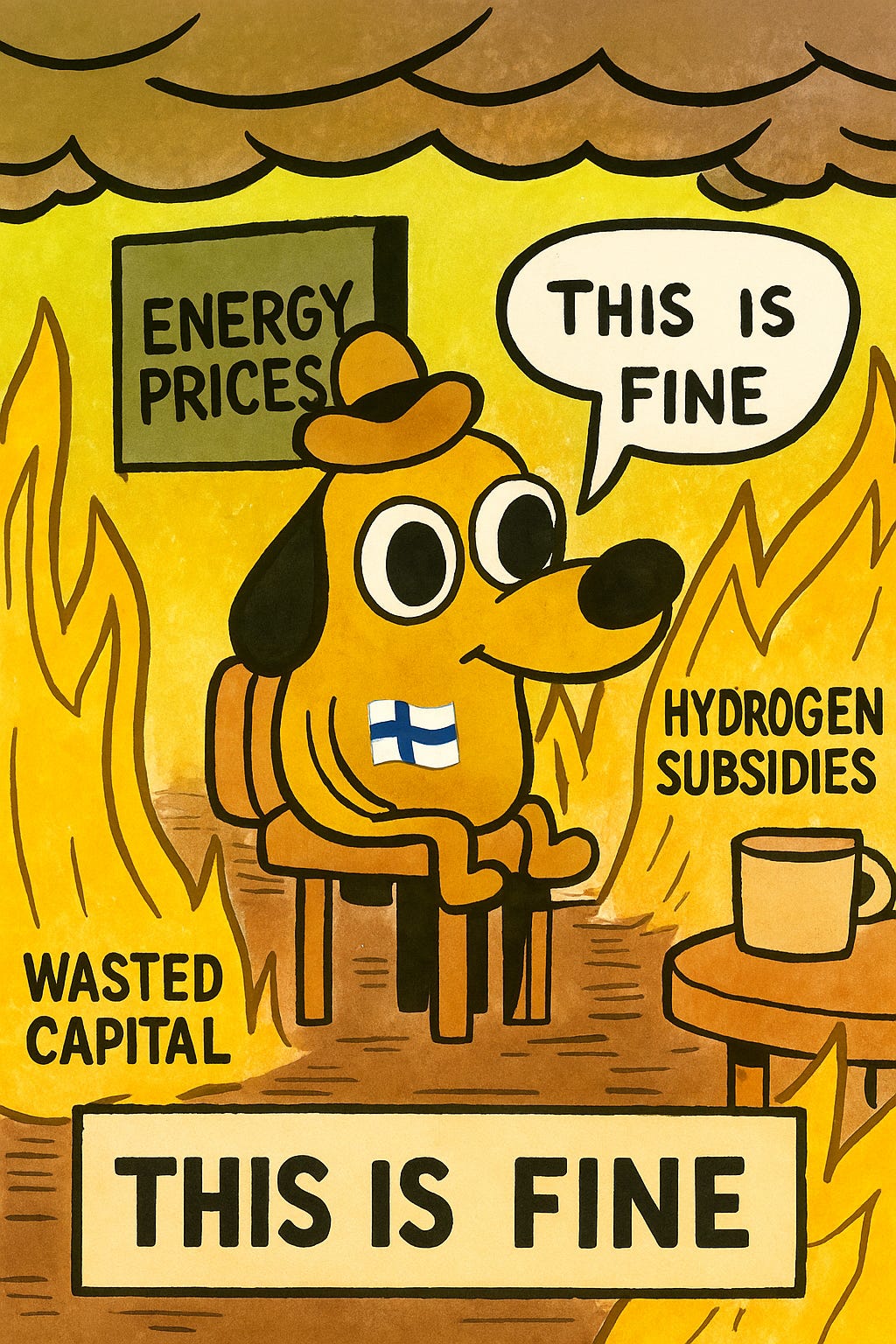
New brave Finland - Hydrogen economy (1)
Launch event: free champagne, no customers. Taxpayers pay.
“Finland’s hydrogen economy is stuttering - there’s still no real market for it, so officials insist it must be manufactured with policy decrees and taxpayer subsidies.”
“Once science has to serve, not truth, but the interests of a state, argument exists only to vindicate the approved belief.” — The Road to Serfdom, ch. 11
Malinvestment Musical. Subsidies shuffle capital from things consumers actually want, such as lower electricity prices. Healthcare that works? I honestly don’t even know; Finnish people have become lazy and idiotic.
The Cantillon effect from this “green stimulus” showers money on consultants and lobbyists first; the average worker gets the hangover in the form of higher power bills and grocery prices.
Only companies living on subsidies call it “the future.”
(Sometimes I wish I was an engineer so I could do shit instead of just whining like a proper economist. At least then I could build something useful instead of just talking shit. Even with my limited knowledge of physics, I understand hydrogen is an inefficient way to store electricity - the laws of thermodynamics don't care about government subsidies.)
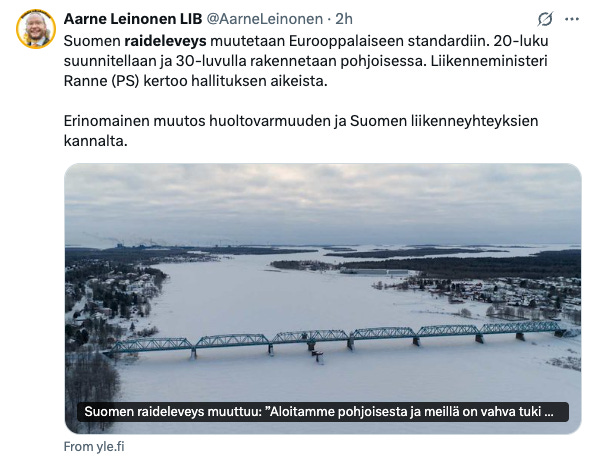
Hurray, we love the railways (2)
NATO will bring investments to Finland - Hurray!
We must rip up perfectly good tracks so we can afford to move troops we can no longer afford.
War talk has clouded judgment: when “national security” is the slogan, cost-benefit math is treason. As Hayek warned, the road to serfdom is always paved with strategic necessity.
-
What, exactly, is a "sufficient" defense for five million Finns? (Asking this here makes you a Russian Bot, though I don't like Russia or Putin.)
-
Who decides when the price tag crosses from prudent to reckless?
If hatred of an external foe sets every budget line, freedom and prosperity shrink to the margins.
In other words, the track to “strategic readiness” can be the same track to serfdom -just painted NATO blue.
When an economy flat-lines for 17 years, nothing says “revival” like swapping 1,435 mm of track for 1,520 mm - and calling it growth.
Finnish economists and "liberalists" are celebrating this? (pics in the end, can't read that X much, it has become so idiotic).
l

The Ministry of Transport has estimated that the cost of conversion work for the railway section between Haparanda and Oulu alone will exceed 1.5 billion euros. The distance is about 150 kilometers. (ESTIMATION…)
New Brave Finland – Datacenter Dissonance (3)
Well, our little minister was not involved so bad, bad, and bad!
Apparently, the box is evil if it says TikTok, but awesome if the logo reads Meta or Google. Hey, all of them are shit, just producing brain rot and stealing our data.
Low temps, reliable grid, sparse population - Finland is a logical server-farm host (shithole). But let's call it what it is: a capital-intensive, low-employment utility business. Selling it as a "high-tech jobs boom" is wishful accounting. The politicians like to yell that these investments are "Billions and Billions," yes, but how much stays in Finland? Some construction jobs and a handful of cleaners? Fucking exquisite.
"Digital Red Menace!" Lohjalainen Harri panics about Chinese bytes corrupting Finnish soil. His brilliant plan? Pray the project fails "Lohjan malliin." Nothing says "economic prosperity" like hoping jobs don't materialize! Peak Finnish paradox: pray for investments and fumble them with bureaucracy or nationalist paranoia.
What cybersecurity threat do these server farms pose to Finland? Absolutely fucking none. The data doesn't care where it sits. TikTok videos don't turn into communist spies when stored in Kouvola/Lohja. Absurd and idiotic.
Yes TikTok is brainrot and stupid shit, you have to be an idiot to install that app on your phone, but it's consumer choice - if you want it then go for it, fucking idiot. Same goes for Facebook, Instagram, all that dopamine garbage.
The Datacenter Paradox: Finland needs investment but fears investors. It celebrates clean industry then hyperventilates about who owns the servers. Classic malinvestment by decree - politicians picking winners.
Datacenters can be fine investments… BUT let's be honest about the tradeoffs. All the value goes abroad. Every megawatt sent to datacenters is not available for households or actual productive industry. Basic economics: when datacenters consume 5-10% of Finland's electricity, prices rise for everyone else. Your heating bill subsidizes Facebook's server cooling. Another brilliant example of the invisible tax of political favoritism.
The Bitcoin Alternative No One Will Discuss: Here's the real irony - datacenters can't be easily switched off during peak demand, creating grid rigidity. Bitcoin mining farms, meanwhile, could be turned on/off based on grid needs, serving as perfect complementary loads for Finland's growing but inconsistent renewable energy (wind/solar). Miners would pay premium rates during excess generation and shut down during shortages - a genuine market solution! But no, can't have sound money solutions in Finland. Better to have Googles servers running 24/7 regardless of grid conditions than allow the evil Bitcoin to improve our renewable energy economics. God forbid we actually use a solution that simultaneously strengthens the grid, supports renewables, AND promotes sound money. That might accidentally lead to common sense, and we can't have that in Finland.
General Observations: The Finnish Decay
Finland is slowly becoming like southern Europe, where nothing gets done on time. We used to laugh at how inefficient and idiotic it is there, but it is now the same here. I got a reply from my Bank after 4-5 months of sending a message. Asking for offers? Wait 3-4 months in some cases (I had this with garbage service). Need a solid service man? Let's see if somebody is free in 2 weeks? Well, I am also becoming like this with my business; nobody even cares.
Rotting services and entertainment
Hard to imagine our restaurant industry was almost on par with Sweden and Denmark just +5 years ago. Today? How many good restaurants have quit? How many Michelin stars have we lost?
Well, how about concerts? Our biggest stadium this summer will host Iron Maiden in June and Robbie Williams in September. WTF? Even the Baltic states can attract bigger names than Finland, this is becoming total shithole in every aspect.
Why?
COVID, collapsing purchasing power, bureaucracy cancer, tax asphyxiation, war hysteria, sheepish compliance, and state dependency.
The entrepreneurial drive that once built world-leading companies has withered. Why innovate when bureaucrats decide winners? Why take risks when failure is punished extremely hard (lifelong debt prison, and shame) and success is taxed away?
The result: economic stagnation rationalized as "social stability" and "equality."
Economic literacy has collapsed. Even the economists here don't grasp the basic concepts, so how on earth could the average citizen? The scariest part is that they don't even care. They've outsourced their economic thinking to the state, the same way they've outsourced their responsibility and risk management. The blind leading the blind, straight to economic mediocrity.
The Finnish Decay: When Will We Say "Enough"?
It would be a good idea to write a book in a similar style to Lawrence Lepard's Big Print: What Happened To America And How Sound Money Will Fix It.
Make readers mad! Advocate for hard money and small government.
Problems? and What's next? Recession 1990s → Nokia Mirage → Euro‑Zone Handcuffs → GFC & The Silent Depression → Everyday Decay → Complete state dependency or get mad?
A glimmer of hope: Despite the lost decades, there's a spark in Finland's youth. They hustle and show more entrepreneurial spirit, saving habits, and investment interest than their parents.
In 1999, we were a top country in education, technology, healthcare, and debt contracted on top of that we were one of the safest places to live, we didn’t lock the bikes and even the doors…
Now look at us?
When will Finns wake up and say enough?
As Hayek warned: "A movement whose main promise is the relief from responsibility cannot but be antimoral in its effect, however lofty the ideals." We've outsourced our moral obligations to an impersonal state, weakening "both the willingness to bear responsibility and the consciousness that it is our own individual duty."
We need a hard money and personal responsibility renaissance.
Coming soon: "How Sound Money and Small Government Can Save Finland From Its Slow-Motion Suicide"
News and sources:
I recently finished reading F.A. Hayek's "The Road to Serfdom" (1944). The similarities between Hayek's warnings and Finland's current course are striking. Europe and Finland are ramping up defence spending to ridiculous levels, now even talking over 5% GDP levels, which is total insanity. What would be enough for defence? We have little freedoms left here in Finland (and Europe), and in pursuit of “security,” we might lose it all. Central planners who believe they can direct an economy better than market forces are just clowns, from hydrogen to datacenter politics. What market forces have we left in Finland? I can breath freely? Soon that will be taxed too. Next we have CBDC coming up in EU.
I highly recommend reading "The Road to Serfdom." Its analysis of how good intentions lead to economic ruin remains as relevant in 2025 as it was in 1944. I feel like a total idiot for not reading it before.
Read 27 books so far this year, thx for Jack Dorsey “reading challenge” I started this in March, aim was 50 book but now we aim to 100, so fucking good to read books!
New brave Finland - Hydrogen economy (1) ://www.is.fi/kotimaa/art-2000011199663.html
Railways (2): https://yle.fi/a/74-20161549 and https://yle.fi/a/74-20161793
Datacenters (3): https://yle.fi/a/74-20160436
Hope its not russian or Chinese? Harri (4) https://www.hs.fi/suomi/art-2000011229295.html

-
-
 @ 7460b7fd:4fc4e74b
2025-05-17 08:26:13
@ 7460b7fd:4fc4e74b
2025-05-17 08:26:13背景:WhatsApp的号码验证与运营商合作关系
作为一款基于手机号码注册的即时通信应用,WhatsApp的账号验证严重依赖全球电信运营商提供的短信或电话服务。这意味着,当用户注册或在新设备登录WhatsApp时,WhatsApp通常会向用户的手机号码发送SMS短信验证码或发起语音电话验证。这一流程利用了传统电信网络的基础设施,例如通过SS7(信令系统7)协议在全球范围内路由短信和电话securityaffairs.com。换句话说,WhatsApp把初始账户验证的安全性建立在电信运营商网络之上。然而,这种依赖关系也带来了隐患:攻击者可以利用电信网络的漏洞来拦截验证码。例如,研究人员早在2016年就演示过利用SS7协议漏洞拦截WhatsApp和Telegram的验证短信,从而劫持用户账户的攻击方法securityaffairs.com。由于SS7协议在全球范围内连接各国运营商,一个运营商的安全缺陷或恶意行为都可能被不法分子利用来获取他网用户的短信验证码securityaffairs.com。正因如此,有安全专家指出,仅依赖短信验证不足以保障账户安全,WhatsApp等服务提供商需要考虑引入额外机制来核实用户身份securityaffairs.com。
除了技术漏洞,基于电信运营商的验证还受到各地政策和网络环境影响。WhatsApp必须与全球各地运营商“合作”,才能将验证码送达到用户手机。然而这种“合作”在某些国家可能并不顺畅,典型例子就是中国。在中国大陆,国际短信和跨境电话常受到严格管控,WhatsApp在发送验证码时可能遭遇拦截或延迟sohu.com。因此,理解WhatsApp在中国的特殊联网和验证要求,需要将其全球验证机制与中国的电信政策和网络审查环境联系起来。下文将深入探讨为什么在中国使用WhatsApp进行号码验证时,必须开启蜂窝移动数据,并分析其中的技术逻辑和政策因素。
中国环境下的特殊问题:为何必须开启蜂窝数据?
中国的网络审查与封锁: WhatsApp自2017年起就在中国大陆遭遇严格封锁。起初,WhatsApp在华的服务受到**“GFW”(防火长城)**的部分干扰——例如曾一度只能发送文本消息,语音、视频和图片消息被封锁theguardian.com。到2017年下半年,封锁升级,很多用户报告在中国完全无法使用WhatsApp收发任何消息theguardian.com。中国官方将WhatsApp与Facebook、Telegram等西方通信平台一同屏蔽,视作对国家网络主权的挑战theguardian.com。鉴于此,在中国境内直接访问WhatsApp的服务器(无论通过Wi-Fi还是本地互联网)都会被防火长城所阻断。即使用户收到了短信验证码,WhatsApp客户端也无法在没有特殊连接手段的情况下与服务器完成验证通信。因此,单纯依赖Wi-Fi等本地网络环境往往无法完成WhatsApp的注册或登陆。很多用户经验表明,在中国使用WhatsApp时需要借助VPN等工具绕过审查,同时尽可能避免走被审查的网络路径sohu.com。
强制Wi-Fi热点与连接策略: 除了国家级的封锁,用户所连接的局域网络也可能影响WhatsApp验证。许多公共Wi-Fi(如机场、商场)采取强制门户认证(captive portal),用户需登录认证后才能上网。对此,WhatsApp在客户端内置了检测机制,当发现设备连入这类强制Wi-Fi热点而无法访问互联网时,会提示用户忽略该Wi-Fi并改用移动数据faq.whatsapp.com。WhatsApp要求对此授予读取Wi-Fi状态的权限,以便在检测到被拦截时自动切换网络faq.whatsapp.com。对于中国用户来说,即便所连Wi-Fi本身联网正常,由于GFW的存在WhatsApp依然可能视之为“不通畅”的网络环境。这也是WhatsApp官方指南中强调:如果Wi-Fi网络无法连接WhatsApp服务,应直接切换到手机的移动数据网络faq.whatsapp.com。在中国,由于本地宽带网络对WhatsApp的封锁,蜂窝数据反而成为相对可靠的通道——尤其在搭配VPN时,可以避开本地ISP的审查策略,实现与WhatsApp服务器的通信sohu.com。
国际短信的运营商限制: 使用移动数据还有助于解决短信验证码接收难题。中国的手机运营商出于防垃圾短信和安全考虑,默认对国际短信和境外来电进行一定限制。许多中国用户发现,注册WhatsApp时迟迟收不到验证码短信,原因可能在于运营商将来自国外服务号码的短信拦截或过滤sohu.com。例如,中国移动默认关闭国际短信接收,需要用户主动发送短信指令申请开通sohu.com。具体而言,中国移动用户需发送文本“11111”到10086(或10085)来开通国际短信收发权限;中国联通和电信用户也被建议联系运营商确认未屏蔽国际短信sohu.com。若未进行这些设置,WhatsApp发送的验证码短信可能根本无法抵达用户手机。在这种情况下,WhatsApp提供的备用方案是语音电话验证,即通过国际电话拨打用户号码并播报验证码。然而境外来电在中国也可能遭到运营商的安全拦截,特别是当号码被认为可疑时zhuanlan.zhihu.com。因此,中国用户经常被建议开启手机的蜂窝数据和漫游功能,以提高验证码接收的成功率sohu.com。一方面,开启数据漫游意味着用户准备接受来自境外的通信(通常也包含短信/电话);另一方面,在数据联网的状态下,WhatsApp可以尝试通过网络直接完成验证通信,从而减少对SMS的依赖。
移动数据的网络路径优势: 在实际案例中,一些中国WhatsApp用户报告仅在开启蜂窝数据的情况下才能完成验证。这可能归因于蜂窝网络和宽带网络在国际出口上的差异。中国移动、联通等运营商的移动数据可能走与宽带不同的网关路由,有时对跨境小流量的拦截相对宽松。此外,WhatsApp在移动数据环境中可以利用一些底层网络特性。例如,WhatsApp可能通过移动网络发起某些专用请求或利用运营商提供的号码归属地信息进行辅助验证(虽然具体实现未公开,但这是业界讨论的可能性)。总之,在中国特殊的网络环境下,开启蜂窝数据是确保WhatsApp验证流程顺利的重要一步。这一步不仅是为了基本的互联网连接,也是为了绕开种种对国际短信和应用数据的拦截限制,从而与WhatsApp的全球基础设施建立必要的通讯。
PDP Context与IMSI:移动网络验证的技术细节
要理解为什么移动数据对WhatsApp验证如此关键,有必要了解移动通信网络中的一些技术细节,包括PDP Context和IMSI的概念。
PDP Context(分组数据协议上下文): 当手机通过蜂窝网络使用数据(如4G/5G上网)时,必须先在运营商核心网中建立一个PDP上下文。这实际上就是申请开启一个数据会话,运营商将为设备分配一个IP地址,并允许其通过移动核心网访问互联网datascientest.com。PDP上下文包含了一系列参数(例如APN接入点名称、QoS等级等),描述该数据会话的属性datascientest.comdatascientest.com。简单来说,激活蜂窝数据就意味着创建了PDP上下文,设备获得了移动网络网关分配的IP地址,可以收发数据包。对于WhatsApp验证而言,只有在建立数据连接后,手机才能直接与WhatsApp的服务器交换数据,例如提交验证码、完成加密密钥协商等。如果仅有Wi-Fi而蜂窝数据关闭,且Wi-Fi环境无法连通WhatsApp服务器,那么验证过程将陷入停滞。因此,在中国场景下,开启蜂窝数据(即建立PDP数据通路)是WhatsApp客户端尝试绕过Wi-Fi限制、直接通过移动网络进行验证通信的前提faq.whatsapp.comsohu.com。值得一提的是,PDP Context的建立也表明手机在运营商网络上处于活跃状态,这对于某些验证机制(比如后述的闪信/闪呼)来说至关重要。
IMSI与MSISDN: IMSI(国际移动用户标识)和MSISDN(移动用户号码,即手机号码)是运营商网络中两个密切相关但不同的标识。IMSI是存储在SIM卡上的一串唯一数字,用于在移动网络中标识用户身份netmanias.com。当手机接入网络时,它向运营商提供IMSI以进行鉴权,运营商据此知道“是哪张SIM”的请求netmanias.com。而MSISDN则是我们平常说的手机号,用于在语音通话和短信路由中定位用户,也存储在运营商的HLR/HSS数据库中netmanias.com。运营商通过IMSI<->MSISDN的对应关系,将来自全球的短信/电话正确路由到用户手机上。WhatsApp的验证短信或电话本质上就是通过目标号码(MSISDN)寻找所属运营商网络,由该网络根据IMSI定位用户终端。一般情况下,WhatsApp应用并不直接接触IMSI这种信息,因为IMSI属于运营商网络的内部标识。然而,IMSI的存在仍然对安全产生影响。例如,**SIM卡交换(SIM Swap)**欺诈发生时,攻击者获得了受害者号码的新SIM卡,新SIM卡会有不同的IMSI,但MSISDN保持原号码不变。运营商会将原号码映射到新的IMSI,这样验证码短信就发送到了攻击者手中的SIM上。对WhatsApp而言,除非有机制检测IMSI变动,否则无法察觉用户号码背后的SIM已被盗换。部分应用在检测到SIM变化时会提示用户重新验证,这需要读取设备的IMSI信息进行比对。然而,在现代智能手机中,获取IMSI通常需要特殊权限,WhatsApp并未明确说明它有此类检测。因此,从WhatsApp角度,IMSI更多是网络侧的概念,但它提醒我们:电信级身份验证依赖于SIM的有效性。只有当正确的IMSI在网络注册、并建立了PDP数据上下文时,WhatsApp的后台服务才能确认该SIM对应的号码目前“在线”,进而可靠地发送验证信号(短信或电话)到该设备。
移动网络的信号辅助验证: 有观点认为,一些OTT应用可能利用移动网络提供的附加服务来辅助号码验证。例如,某些运营商提供号码快速验证API,当应用检测到设备在移动数据网络中时,可以向特定地址发起请求,由运营商返回当前设备的号码信息(通常通过已经建立的PDP通道)。Google等公司在部分国家与运营商合作过类似服务,实现用户免输入验证码自动完成验证。但就WhatsApp而言,没有公开证据表明其使用了运营商提供的自动号码识别API。即便如此,WhatsApp鼓励用户保持移动网络在线的做法,隐含的意义之一可能是:当手机处于蜂窝网络且数据畅通时,验证码通过率和验证成功率都会显著提升。这既包括了物理层面短信、电话能否送达,也涵盖了数据层面应用和服务器能否互通。
Flash Call机制:WhatsApp验证的新方案
针对传统SMS验证码容易被拦截、延迟以及用户体验不佳的问题,WhatsApp近年来引入了一种Flash Call(闪呼)验证机制fossbytes.com。所谓闪呼,即应用在用户验证阶段向用户的手机号发起一个非常短暂的来电:用户无需真正接听,WhatsApp会自动结束这通电话,并根据通话记录来确认是否拨通fossbytes.com。
原理与流程: 当用户选择使用闪呼验证(目前主要在Android设备上可用),WhatsApp会请求权限访问用户的通话记录fossbytes.com。随后应用拨打用户的号码,一般是一个预先设定的特定号码或号码段。由于WhatsApp后台知道它拨出的号码及通话ID,只要该未接来电出现在用户手机的通话日志中,应用即可读取并匹配最后一通来电的号码是否符合验证要求,从而确认用户持有这个号码fossbytes.com。整个过程用户无需手动输入验证码,验证通话在数秒内完成。相比6位数字短信验证码需要用户在短信和应用间切换输入,闪呼方式更加快捷无缝fossbytes.com。
优缺点分析: 闪呼验证的优势在于速度快且避免了SMS可能的延迟或拦截。一些分析指出闪呼将成为取代SMS OTP(一次性密码)的新趋势,Juniper Research预测2022年用于验证的闪呼次数将从2021年的六千万猛增到五十亿次subex.comglobaltelcoconsult.com。对于WhatsApp这样全球用户庞大的应用,闪呼可以节约大量SMS网关费用,并绕开部分运营商对国际SMS的限制。然而,闪呼也有局限:fossbytes.com首先,iOS设备由于系统安全限制,应用无法访问通话记录,因此iPhone上无法使用闪呼验证fossbytes.com。这意味着苹果用户仍需使用传统短信验证码。其次,为实现自动匹配来电号码,用户必须授予读取通话记录的权限,这在隐私上引发一些担忧fossbytes.comfossbytes.com。WhatsApp声称不会将通话记录用于验证以外的用途,号码匹配也在本地完成fossbytes.com,但考虑到母公司Meta的隐私争议,部分用户依然顾虑。第三,闪呼验证依赖语音通话路线,同样受制于电信网络质量。如果用户所处网络无法接通国际来电(比如被运营商拦截境外短振铃电话),闪呼也无法成功。此外,从运营商角度看,闪呼绕过了A2P短信计费,可能侵蚀短信营收,一些运营商开始研究识别闪呼流量的策略wholesale.orange.com。总体而言,闪呼机制体现了WhatsApp希望减轻对短信依赖的努力,它在许多国家提升了验证体验,但在中国等特殊环境,其效果仍取决于本地语音网络的开放程度。值得注意的是,中国运营商对于境外电话,尤其是这种**“零响铃”未接来电**也有防范措施,中国电信和联通用户就被建议如需接收海外来电验证,应联系客服确保未拦截海外来电hqsmartcloud.com。因此,即便WhatsApp支持闪呼,中国用户若未开启移动语音漫游或运营商许可,仍然难以通过此途径完成验证。
与SIM Swap安全性的关系: 从安全角度看,闪呼并未实质提升抵御SIM交换攻击的能力。如果攻击者成功将受害者的号码转移至自己的SIM卡上(获取新IMSI),那么无论验证码以短信还是闪呼方式发送,都会到达攻击者设备。闪呼机制能防御的是部分恶意拦截短信的行为(如恶意网关或木马读取短信),但对社工换卡没有太大帮助。WhatsApp早已提供两步验证(即设置6位PIN码)供用户自行启用,以防号码被他人重新注册时需要额外密码。然而大量用户未开启该功能。因此,闪呼更多是从用户体验和成本出发的改良,而非针对高级别攻击的防护机制。正如前文所述,真正要防御SIM Swap和SS7漏洞等系统性风险,依赖运营商的号码验证本身就是薄弱环节,需要引入更高级的身份认证手段。
SIM卡交换攻击的风险与运营商信任问题
WhatsApp和Telegram一类基于手机号认证的应用普遍面临一个安全挑战:手机号码本身并非绝对安全的身份凭证。攻击者可以通过一系列手段取得用户的号码控制权,其中SIM交换(SIM Swap)是近年高发的欺诈手法。SIM Swap通常由不法分子冒充用户,诱骗或贿赂运营商客服将目标号码的服务转移到攻击者的新SIM卡上keepnetlabs.com。一旦成功,所有发往该号码的短信和电话都转由攻击者接收,原机主的SIM卡失效。对于依赖短信/电话验证的应用来说,这意味着攻击者可以轻易获取验证码,从而重置账户并登录。近年来全球SIM Swap案件呈上升趋势,许多在线服务的账号被此攻破rte.ie。
WhatsApp并非未知晓此风险。事实上,WhatsApp在其帮助中心和安全博客中多次提醒用户开启两步验证PIN,并强调绝不向他人透露短信验证码。然而,从系统设计上讲,WhatsApp仍将信任根基放在运营商发送到用户手机的那串数字验证码上。一旦运营商端的安全被绕过(无论是内部员工作恶、社工欺诈,还是SS7网络被黑客利用securityaffairs.com),WhatsApp本身无法辨别验证码接收者是否是真正的用户。正如安全研究所Positive Technologies指出的那样,目前主要的即时通讯服务(包括WhatsApp和Telegram)依赖SMS作为主要验证机制,这使得黑客能够通过攻击电信信令网络来接管用户账户securityaffairs.com。换言之,WhatsApp被迫信任每一个参与短信/电话路由的运营商,但这个信任链条上任何薄弱环节都可能遭到利用securityaffairs.com。例如,在SIM Swap攻击中,运营商本身成为被欺骗的对象;而在SS7定位拦截攻击中,全球互联的电信网成为攻击面。在中国的场景下,虽然主要威胁来自审查而非黑客,但本质上仍是WhatsApp无法完全掌控电信网络这一事实所导致的问题。
应对这些风险,WhatsApp和Telegram等采用了一些弥补措施。除了提供用户自行设定的二次密码,两者也开始探索设备多因子的概念(如后文Telegram部分所述,利用已有登录设备确认新登录)。然而,对绝大多数首次注册或更换设备的用户来说,传统的短信/电话验证仍是唯一途径。这就是为什么在高安全需求的行业中,SMS OTP正逐渐被视为不充分securityaffairs.com。监管机构和安全专家建议对涉敏感操作采用更强验证,如专用身份应用、硬件令牌或生物识别等。WhatsApp作为大众通信工具,目前平衡了易用性与安全性,但其依赖电信运营商的验证模式在像中国这样特殊的环境下,既遇到政策阻碍,也隐藏安全短板。这一点对于决策制定者评估国外通信应用在华风险时,是一个重要考量:任何全球运营商合作机制,在中国境内都可能因为**“最后一公里”由中国运营商执行**而受到影响。无论是被拦截信息还是可能的监控窃听,这些风险都源自于底层通信网的控制权不在应用服务商手中。
Telegram登录机制的比较
作为对比,Telegram的账号登录机制与WhatsApp类似,也以手机号码为主要身份标识,但在具体实现上有一些不同之处。
多设备登录与云端代码: Telegram从设计上支持多设备同时在线(手机、平板、PC等),并将聊天内容储存在云端。这带来的一个直接好处是:当用户在新设备上登录时,Telegram会优先通过已登录的其他设备发送登录验证码。例如,用户尝试在电脑上登录Telegram,Telegram会在用户手机上的Telegram应用里推送一条消息包含登录码,而不是立即发短信accountboy.comaccountboy.com。用户只需在新设备输入从老设备上收到的代码即可完成登录。这种机制确保了只要用户至少有一个设备在线,就几乎不需要依赖运营商短信。当然,如果用户当前只有一部新设备(例如换了手机且旧设备不上线),Telegram才会退而求其次,通过SMS发送验证码到手机号。同时,Telegram也允许用户选择语音电话获取验证码,类似于WhatsApp的语音验证。当用户完全无法收到SMS时(比如在中国这种场景),语音呼叫常常比短信更可靠seatuo.com。
两步验证密码: 与WhatsApp一样,Telegram提供可选的两步验证密码。当启用此功能后,即使拿到短信验证码,仍需输入用户设置的密码才能登录账户quora.com。这对抗SIM Swap等攻击提供了另一层防线。不过需要指出,如果用户忘记了设置的Telegram密码且没有设置信任邮箱,可能会永久失去账号访问,因此开启该功能在中国用户中接受度一般。
登录体验与安全性的取舍: Telegram的登录流程在用户体验上更加灵活。多设备下无需每次都收验证码,提高了便利性。但从安全角度看,这种“信任已有设备”的做法也有隐患:如果用户的某个设备落入他人之手并未及时登出,那么该人有可能利用该设备获取新的登录验证码。因此Telegram会在应用中提供管理活动会话的功能,用户可随时查看和撤销其它设备的登录状态telegram.org。总体而言,Telegram和WhatsApp在初始注册环节同样依赖短信/电话,在这一点上,中国的网络环境对两者影响相似:Telegram在中国同样被全面封锁,需要VPN才能使用,其短信验证码发送也会受到运营商限制。另外,Telegram曾在2015年因恐怖分子利用该平台传递信息而被中国当局重点关注并屏蔽,因此其国内可达性甚至比WhatsApp更低。许多中国用户实际使用Telegram时,通常绑定国外号码或通过海外SIM卡来收取验证码,以绕开国内运营商的限制。
差异总结: 简而言之,Telegram在登录验证机制上的主要优势在于已有会话协助和云端同步。这使得老用户换设备时不依赖国内短信通道即可登录(前提是原设备已登录并可访问)。WhatsApp直到最近才推出多设备功能,但其多设备模式采用的是端到端加密设备链路,需要主手机扫码授权,而非像Telegram那样用账号密码登录其它设备。因此WhatsApp仍然强绑定SIM卡设备,首次注册和更换手机号时逃不开运营商环节。安全方面,两者的SMS验证所面临的系统性风险(如SS7攻击、SIM Swap)并无本质区别,都必须仰仗运营商加强对核心网络的保护,以及用户自身启用附加验证措施securityaffairs.comkeepnetlabs.com。
结论
对于希望在中国使用WhatsApp的用户来说,“开启蜂窝数据”这一要求背后体现的是技术与政策交织的复杂现实。一方面,蜂窝数据承载着WhatsApp与其全球服务器通信的关键信道,在中国的受限网络中提供了相对可靠的出路faq.whatsapp.comsohu.com。另一方面,WhatsApp的号码验证机制深深植根于传统电信体系,必须经由全球运营商的“协作”才能完成用户身份确认securityaffairs.com。而在中国,这种协作受到防火长城和运营商政策的双重阻碍:国际短信被拦截、国际数据被阻断。为克服这些障碍,WhatsApp既采取了工程上的应对(如检测强制Wi-Fi并提示使用移动网络faq.whatsapp.com),也引入了诸如闪呼验证等新方案以减少对短信的依赖fossbytes.com。但从根本上说,只要注册流程离不开手机号码,这种与电信运营商的捆绑关系就无法割舍。由此带来的安全问题(如SIM Swap和信令网络漏洞)在全球范围内敲响警钟securityaffairs.comkeepnetlabs.com。
对于从事安全研究和政策评估的人士,这篇分析揭示了WhatsApp在中国遇到的典型困境:技术系统的全球化与监管环境的本地化冲突。WhatsApp全球统一的验证框架在中国水土不服,不得不通过额外的设置和手段来“曲线救国”。这既包括让用户切换网络、配置VPN等绕过审查,也包括思考未来是否有必要采用更安全独立的验证方式。相比之下,Telegram的机制给出了一种启示:灵活运用多设备和云服务,至少在一定程度上降低对单一短信渠道的依赖。然而,Telegram自身在中国的处境表明,再优雅的技术方案也难以直接对抗高强度的网络封锁。最终,无论是WhatsApp还是Telegram,要想在受限环境下可靠运作,都需要技术与政策的双管齐下:一方面提高验证与登录的安全性和多样性,另一方面寻求运营商和监管层面的理解与配合。
综上所述,WhatsApp要求中国用户开启蜂窝数据并非偶然的臆想,而是其全球运营商合作验证机制在中国受阻后的务实选择。这一要求折射出移动通信应用在跨境运营中面临的挑战,也提醒我们在设计安全策略时必须考虑底层依赖的信任假设。对于个人用户,最实际的建议是在使用此类应用时提前了解并遵循这些特殊设置(如开通国际短信、启用数据漫游),并善用应用自身的安全功能(如两步验证)来保护账户免遭社工和网络攻击keepnetlabs.com。对于监管和运营商,则有必要权衡安全审查与用户便利之间的平衡,在可控范围内为可信的全球服务留出技术通道。在全球通信愈加融合的时代,WhatsApp的中国验证问题或许只是一个缩影,背后涉及的既有网络安全考量,也有数字主权与国际合作的议题,值得持续深入研究和关注。
faq.whatsapp.comfossbytes.comtheguardian.comsecurityaffairs.comsecurityaffairs.comkeepnetlabs.comdatascientest.comnetmanias.comsohu.comsohu.com
-
 @ 609f186c:0aa4e8af
2025-05-16 20:57:43
@ 609f186c:0aa4e8af
2025-05-16 20:57:43Google says that Android 16 is slated to feature an optional high security mode. Cool.
Advanced Protection has a bunch of requested features that address the kinds of threats we worry about.
It's the kind of 'turn this one thing on if you face elevated risk' that we've been asking for from Google.
And likely reflects some learning after Google watched Apple 's Lockdown Mode play out. I see a lot of value in this..
Here are some features I'm excited to see play out:
The Intrusion Logging feature is interesting & is going to impose substantial cost on attackers trying to hide evidence of exploitation. Logs get e2ee encrypted into the cloud. This one is spicy.
The Offline Lock, Inactivity Reboot & USB protection will frustrate non-consensual attempts to physically grab device data.

Memory Tagging Extension is going to make a lot of attack & exploitation categories harder.
2G Network Protection & disabling Auto-connect to insecure networks are going to address categories of threat from things like IMSI catchers & hostile WiFi.
I'm curious about some other features such as:
Spam & Scam detection: Google messages feature that suggests message content awareness and some kind of scanning.
Scam detection for Phone by Google is interesting & coming later. The way it is described suggests phone conversation awareness. This also addresses a different category of threat than the stuff above. I can see it addressing a whole category of bad things that regular users (& high risk ones too!) face. Will be curious how privacy is addressed or if this done purely locally. Getting messy: Friction points? I see Google thinking these through, but I'm going to add a potential concern: what will users do when they encounter friction? Will they turn this off & forget to re-enable? We've seen users turn off iOS Lockdown Mode when they run into friction for specific websites or, say, legacy WiFi. They then forget to turn it back on. And stay vulnerable.

Bottom line: users disabling Apple's Lockdown Mode for a temporary thing & leaving it off because they forget to turn it on happens a lot. This is a serious % of users in my experience...
And should be factored into design decisions for similar modes. I feel like a good balance is a 'snooze button' or equivalent so that users can disable all/some features for a brief few minute period to do something they need to do, and then auto re-enable.
Winding up:
I'm excited to see how Android Advanced Protection plays with high risk users' experiences. I'm also super curious whether the spam/scam detection features may also be helpful to more vulnerable users (think: aging seniors)...
Niche but important:
Some users, esp. those that migrated to security & privacy-focused Android distros because of because of the absence of such a feature are clear candidates for it... But they may also voice privacy concerns around some of the screening features. Clear communication from the Google Security / Android team will be key here.
-
 @ 866e0139:6a9334e5
2025-05-17 08:24:02
@ 866e0139:6a9334e5
2025-05-17 08:24:02Autor: Lilly Gebert. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Teil 1 des Artikels lesen Sie hier.
Wo Begehren herrscht, bleibt wahre Begegnung aus. Entsteht Frieden in der Sexualität doch immer erst dort, wo das Wollen endet und reines Sein beginnt. Hier wird die Vereinigung nicht länger als Erfüllung eines Mangels erfahren, sondern als Ausdruck innerer Fülle. In diesem Wandel offenbart sich die Liebe als ein Weg zur Wahrheit und damit als Anleitung zum Frieden.
Der Ursprung der Trennung als Anfang vom Krieg
In dem Sinne, wie der erste Teil dieses Texts mit dem Ausblick auf die Fähigkeit des Einzelnen endete, Angst und Abwehr abzubauen, sich selbst zu spüren – und andere nicht als Bedrohung, sondern als lebendige Gegenüber wahrzunehmen, beginnt dieser Text mit der Frage, warum wir dazu nicht mehr in der Lage zu sein scheinen? Wo ist die Lebendigkeit? Warum können wir sie weder in uns, noch in anderen annehmen?
Folgen wir dem australischen Autor Barry Long, so finden sexuelle Frustration wie Krieg ihrer beiden Ursprung darin, dass der Mann seine göttliche Stellung gegenüber der Frau eingebüßt hat und sie aufgrund dessen körperlich nicht mehr erreichen kann. Er sei es, der vergessen hat, wie man liebt und dadurch seine ursprüngliche, göttliche Autorität aufgegeben und die sexuelle Kontrolle über sich verloren hat. Was daraus entstanden sei, sei die beständige Unzufriedenheit in der Frau und eine ständige Ruhelosigkeit im Mann, derer beider eigentliches Leiden keiner von beiden mehr zuordnen kann. Zu abgeschnitten und korrumpiert sei derweilen die Vorstellung der Frau, ein Liebesakt könne ihre feinsten und tiefsten Energien sammeln und freisetzen.
Was beide stattdessen täten, sei diese Energien zu verdrehen und sie stattdessen in Sexbesessenheit, in zwanghaftem sexuellen Fantasieren sowie chronischem Onanieren «auszuleben», oder gleich ganz zu unterdrücken, was zweifelsohne zu Wut und Gewalt führe, wie auch universelle Symptome wie Arbeitswut oder die Gier nach Geld mit sich zöge. Womit wir, nebenbei bemerkt, auch wieder bei Fromm sind, für den unsere Konsumgesellschaft ebenfalls nur ein Deckmantel für unsere Unfähigkeit zu lieben oder gar unsere Furcht vor der Liebe war. Was diese Vernachlässigung der Liebe als Vernachlässigung der Frau wiederum laut Long beim Mann auslöse, sei jene Spirale aus vorzeitiger Ejakulation, Schuldgefühlen, Ängstlichkeit, Selbstzweifeln, Impotenz, sexueller Verkümmerung, die sich als sexuelles Desinteresse maskiert, sexuelle Abstinenz aufgrund von unterdrückter Versagensangst, sexueller Angeberei und Mangel an wahrem Wissen. All dies, schreibt Long, mute «er der Frau zu und verschlimmert damit ihre grundlegende Unzufriedenheit und seine eigene Unruhe». Für den Mann sei dies, als würde er sein inneres Leiden zum Leben erwecken: Für ihn sei «die weibliche Furie der Emotion die Hölle auf Erden. Dies ist der Teil in ihr, mit dem er nicht umgehen und den er nicht verstehen kann. Der Dämon seines eigenen Versagens in der Liebe wird lebendig, um ihn zu verschmähen, herunterzumachen und zu quälen.»
Wiederum nicht selten jedoch gäbe der Mann, des lieben Friedens willen, auf – und damit die letzten Überreste seiner Männlichkeit und Autorität. Dann, so Long «werden beide gemeinsam alt und fühlen sich sicher, aber halb tot, indem sie sich in der schrecklichen Welt des Kompromisses aufeinander stützen». Dabei wird «die Furie den Mann nie sein Versagen, die Frau richtig zu lieben, vergessen lassen». Die Frau, so stellt Long hervor, «muss geliebt werden». Die Zukunft der Menschheit hänge davon ab, «dass die Frau geliebt wird. Denn nur wenn die Frau wirklich geliebt wird, kann der Mann wirklich er selbst sein und seine verlorene Autorität zurückgewinnen. Nur dann kann auf Erden wieder Frieden einkehren. Doch die Frau, wie sie jetzt ist, kann nicht lange oder für immer – von dem Mann, wie er jetzt ist, geliebt werden. Zusammen sind sie in einem Teufelskreis gefangen. Und wenn sie ihren eigenen Vorstellungen von der Liebe überlassen werden, gibt es keinen Ausweg.»
Was einst Liebe war
Ursprünglich, so Long, verkörperten Mann und Frau zwei Pole reiner spiritueller Liebe: Die Frau war der heitere, empfangende Ausdruck reiner Liebe, der Mann der aktive, schützende Pol, dessen Autorität der Bewahrung dieser göttlichen Qualität diente. Ihre Kommunikation geschah durch ein goldenes Energiefeld – die Glorie –, das sie in stiller, unmittelbarer Verbindung hielt, unabhängig von Raum und Zeit. Wenn ihre Energien Erneuerung brauchten, vereinten sie sich körperlich in heiliger Liebe, die sie nicht nur regenerierte, sondern zudem mit Gott verband. Doch mit dem wachsenden Fokus auf den äußeren Aufbau der Welt begannen sie, das unmittelbare Lieben zu vergessen; die Glorie verlor ihre Strahlkraft, Sprache trat an die Stelle wortloser Verständigung, und aus Worten wuchsen Missverständnisse und Entfremdung. Die Frau wurde unzufrieden und verwirrt, der Mann seiner wahren Autorität beraubt, suchte Ersatz durch Macht und zwang die Frau in soziale Unterordnung, was in ihr Zorn und Unversöhnlichkeit entfachte. Damit begann der Wettlauf der Menschheit – ein Weg in die Zeit und fort von der ursprünglichen Einheit.
Dieser Wettlauf um Macht, Zorn und Unterdrückung ist zugleich die Geschichte, wie der Mensch sich selbst zum Wolf wurde und den Krieg gegen sich selbst begann. Um nicht länger an den Verlust seiner einstigen Einheit erinnert zu werden, hat er sich eine Welt geschaffen, die auf der Verwechslung von Liebe mit Manipulation, auf Reiz und Täuschung, wie auch auf der Reduktion von Sexualität auf bloße Befriedigung beruht. Schon fernab jeder Wirklichkeit, flieht er in lieblose Fantasien, Sexträume oder in deren Ausleben durch flüchtige Flirts und wechselnde Partner. Er flieht immer weiter – nur um sich immer weniger eingestehen zu müssen, dass in seinem Leben keine Liebe herrscht. Er tut alles, um der Konfrontation auszuweichen, dass nicht die anderen es sind, sondern er selbst, der keine Verantwortung für die Liebe in seinem Leben übernimmt. Nicht die Welt verweigert ihm die Liebe – er selbst ist es, der noch nicht dafür bereit ist, sich der Wahrheit zu stellen, dass die Liebe im Hier und Jetzt vollzogen werden will und nicht in einer imaginären Zukunft oder einem vulgären Traum.
Wie Liebe entsteht
Das wahre Leben findet in deinem Körper, in deinen Gefühlen und Empfindungen statt – nicht in deinem Kopf. In deinem Kopf kannst Du dir noch so oft und viel einreden, dass Du emanzipiert bist; dass Du auch ohne Partner in deinem Leben auskommst; dass Du emotional-physisch nicht abhängig bist; dass die Partnerschaft, in der Du dich befindest, frei ist; dass das, was Du und dein Partner da miteinander habt, Liebe sei; und dass Du glücklich bist mit dem, was Du für Liebe hältst. Dein Kopf kann das alles. Den leisen Schmerz, die Sehnsucht, dass dir trotz allem etwas fehlt, was kein Gelübte und keine Gelüste werden stillen können – den kannst Du nur fühlen.
Das Wissen um den Ursprung, von dem Du einst getrennt wurdest, ist kein Wissen, das deinem Verstand entspringt. Deshalb kommt für jeden die Zeit – und sie kommt immer schneller –, in der sein Selbst sterben muss, wie alles, was dem Leben unterliegt. Es ist die Zeit, in der Du erkennst, dass dein Verstand keine Brücken baut, sondern Mauern – und dass diese Mauern dich dem Leben nicht näherbringen, sondern es aussperren. Der Moment jedoch, indem Du beginnst, diese Mauern niederzureißen, ist zugleich der Moment, in dem die Liebe tiefer in deinen Körper dringt und dort dein Selbst sich auflöst. In dem nun auch du jemanden in dein Leben lassen kannst, dessen Blicke dich nicht nur anschauen, sondern so sehen, wie auch du ihn siehst, und dessen Berührungen mehr als nur deinen Körper streicheln.
Dieser Prozess ist schmerzhaft und traumatisch; und in einer verwirrten, unwissenden Zeit wie der unseren ist es alles andere als leicht, zum goldenen Zustand der Liebe zurückzukehren. Diesen Weg zu gehen, heißt, verletzlich zu werden: dich nicht länger selbst abzuschneiden oder zu verhärten aus Angst vor alten Wunden. Sondern den Mut aufzubringen, den Weg zu dir selbst zu gehen – zunächst allein, und dann mit jemandem, dessen Liebe reicht, ihn aufrichtig mit dir zu teilen und weiterzugehen. Ohne Spielchen, ohne falsche Egos, ohne die vielen Ersatzbefriedigungen, die uns doch nur weiter von uns selbst entfernen.
Vergeude deine Zeit und Energie also nicht weiter mit jemandem, für den Du nur ein Kompromiss bist, und sei ehrlich gegenüber denjenigen, die dies für dich sind. Stumpf nicht ab an emotionaler Unschärfe oder körperlicher Oberflächlichkeit. Lass’ dir nicht einreden, Du hättest nicht mehr verdient oder könntest nicht mehr geben. Praktiziere die Liebe, die Du selber erfahren willst. Gleich wie jede Veränderung und jeder Frieden vollzieht auch sie sich nur, wenn Du sie nicht inflationär gebrauchst, sondern um ihrer selbst willen lebst. Ihren Weg zu gehen, bedeutet, Verantwortung zu übernehmen. Für die Liebe, aber auch für den Frieden in dieser Welt. Genauso wie die Liebe lässt sich dieser nämlich auch nicht in die Zukunft und ihre möglichen Szenarien verlagern. Frieden ist keine Utopie. Frieden will gelebt werden. Hier, Jetzt und Heute. Und auch nicht von irgendwem anders, sondern von Dir.
Kinder wissen das. Finden sie auch keine Ausreden dafür, warum Frieden jetzt noch nicht möglich sei. Sie sind Frieden. Weil sie den Krieg noch nicht in sich tragen.
Legen also auch wir die Waffen nieder – auf allen Schlachtfeldern, von denen wir als Menschheit glauben, wir müssten sie führen.
Fangen wir lieber an, Frieden mit uns selbst zu schließen.
Wer Barry Longs vollständige «Anleitung zum Sex» lesen möchte, dem empfehle ich die hier zitierte Lektüre von «Sexuelle Liebe auf göttliche Weise».
Lilly Gebert betreibt den Substack-Blog "Treffpunkt im Unendlichen" und schreibt regelmäßig für "die Freien" und Manova. Zuletzt erschien von ihr "Das Gewicht der Welt". Im Herbst erscheint "Sein statt Haben. Enzyklopädie für eine neue Zeit." (vorbestellbar).
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 961e8955:d7fa53e4
2025-05-17 07:35:51
@ 961e8955:d7fa53e4
2025-05-17 07:35:51Cryptocurrencies are digital currencies that have gained significant attention in recent times. Cryptocurrency mining, also known as mining, involves computers equipped with specialized software and hardware solving problems to validate cryptocurrency transfer transactions and, in return, being rewarded with newly generated cryptocurrency. If you have a powerful computer and an internet connection, you can easily engage in mining. Anyone interested in cryptocurrency mining needs to have computers with robust processors.
Transfers between wallets are possible, and transactions can be added to the transaction pool on numerous blockchains without the need for confirmation. Later, transactions are combined to form a block. These blocks are verified from the perspective of the systems connected to the network and, upon confirmation, are added to the blockchain.
To earn money through mining, you need to invest a significant amount of time. Earnings can vary depending on the type of mining, the value of the cryptocurrency, and the unit of measurement. Considerable budget investment is required for the system. Price increases in computer components lead to an increase in investment. However, it's possible to turn your investment into profit in a short period.
Having a high processing power can make it more challenging to cool the computers. Taking this into account, you need to adjust your budget. Additionally, an increase in the number of computers makes monitoring and maintenance more difficult. You must have sufficient knowledge about hardware. Otherwise, there is a risk of your money going to waste. As mining progresses, your investment may need to increase. In the event of malfunctions and decreased performance, replacements are necessary.
How to Earn with Bitcoin Mining? With mining, you can earn cryptocurrency without having to work too hard. Bitcoin is obtained from units called blocks. To complete a block, there is a reward of 12.5 BTC. You can calculate this based on the current value of Bitcoin.
When Bitcoin was first introduced in 2009, mining rewarded 50 BTC. We can say that this number is halved every four years. So, in 2012, it became 25 BTC, in 2015, 12.5 BTC, and as of 2020, it was 6.25 BTC.
How much profit can be made from Bitcoin mining? Earning from cryptocurrencies is not limited to cryptocurrency exchanges. As mentioned earlier, you can also earn through mining. The income and expenses of Bitcoin mining can vary depending on the type of mining performed. Therefore, individuals interested in mining need to make a good plan.
The income can vary depending on the chosen mining method and the price and unit of the cryptocurrency. Making a profit takes time. After purchasing the hardware, you need to wait for it to amortize its cost and recover the fees paid for cloud mining.
Recent price stagnation has led to a decrease in on-chain transaction activity for Bitcoin. This has negatively affected miners' earnings. According to recent data, 231,437 transactions have been processed. This is noted as the lowest number of transactions since May 24th. We can see a 40% drop from the peak of 382,408 transactions in July.
What is the Return on Ethereum Mining? Ethereum is one of the most widely mined cryptocurrencies in the cryptocurrency market. Ethereum miners can earn an average of around $1,121 per year. When you factor in expenses for electricity, other hardware, and various items, it may not be possible to make a significant profit in the first year. However, if you view this as an investment, you can expect to make substantial gains in subsequent periods.
Having powerful hardware increases earnings and enables efficient mining. Just as with all investments, the risk-reward ratio should be calculated carefully for mining
-
 @ b83a28b7:35919450
2025-05-16 19:26:56
@ b83a28b7:35919450
2025-05-16 19:26:56This article was originally part of the sermon of Plebchain Radio Episode 111 (May 2, 2025) that nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpqtvqc82mv8cezhax5r34n4muc2c4pgjz8kaye2smj032nngg52clq7fgefr and I did with nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7ct4w35zumn0wd68yvfwvdhk6tcqyzx4h2fv3n9r6hrnjtcrjw43t0g0cmmrgvjmg525rc8hexkxc0kd2rhtk62 and nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpq4wxtsrj7g2jugh70pfkzjln43vgn4p7655pgky9j9w9d75u465pqahkzd0 of the nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcqyqwfvwrccp4j2xsuuvkwg0y6a20637t6f4cc5zzjkx030dkztt7t5hydajn
Listen to the full episode here:
<<https://fountain.fm/episode/Ln9Ej0zCZ5dEwfo8w2Ho>>
Bitcoin has always been a narrative revolution disguised as code. White paper, cypherpunk lore, pizza‑day legends - every block is a paragraph in the world’s most relentless epic. But code alone rarely converts the skeptic; it’s the camp‑fire myth that slips past the prefrontal cortex and shakes hands with the limbic system. People don’t adopt protocols first - they fall in love with protagonists.
Early adopters heard the white‑paper hymn, but most folks need characters first: a pizza‑day dreamer; a mother in a small country, crushed by the cost of remittance; a Warsaw street vendor swapping złoty for sats. When their arcs land, the brain releases a neurochemical OP_RETURN which says, “I belong in this plot.” That’s the sly roundabout orange pill: conviction smuggled inside catharsis.
That’s why, from 22–25 May in Warsaw’s Kinoteka, the Bitcoin Film Fest is loading its reels with rebellion. Each documentary, drama, and animated rabbit‑hole is a stealth wallet, zipping conviction straight into the feels of anyone still clasped within the cold claw of fiat. You come for the plot, you leave checking block heights.
Here's the clip of the sermon from the episode:
nostr:nevent1qvzqqqqqqypzpwp69zm7fewjp0vkp306adnzt7249ytxhz7mq3w5yc629u6er9zsqqsy43fwz8es2wnn65rh0udc05tumdnx5xagvzd88ptncspmesdqhygcrvpf2
-
 @ 9c9d2765:16f8c2c2
2025-05-17 06:44:56
@ 9c9d2765:16f8c2c2
2025-05-17 06:44:56CHAPTER TWENTY ONE
“Yes, thank you,” he repeated, eyes sharp. “Because in your rejection, I found purpose. In your insults, I found strength. And now, here I stand not as a man shaped by wealth but as a man forged in fire.”
The room went silent. A solemn kind of reverence now filled the air.
“I will not seek revenge,” James continued. “That’s not the legacy I want. But I will hold people accountable. And this… is just the beginning.”
Helen trembled in her seat. Mark felt sweat roll down his back. Even Susan and Robert felt the sting of those words.
“JP Enterprises,” James said, lifting his glass in a toast, “was built on vision, perseverance, and truth. And under my leadership, it will rise higher than ever before. For those willing to build, I welcome you. For those still plotting destruction…”
He let his words hang in the air, cold and final.
“…you won’t last long.”
The crowd erupted into an ovation once again, this time standing as they clapped.
Mrs. JP hugged her son once more. Mr. JP’s proud expression never faltered.
As the celebration continued, Helen slowly rose and left the hall in silence, not from shame but from a new, burning bitterness. Mark followed shortly behind her, furious whispers passing between them.
Tracy stayed seated, her face pale, her hands unmoving. She couldn’t stop replaying James’s words in her mind.
And James? He turned to the side of the stage and saw Rita standing there, tears glistening in her eyes, pride glowing on her face. She had seen the fall. Now she was witnessing the rise.
The moment was thick with silence. All eyes in the grand ballroom turned toward the center of the unfolding drama like magnets drawn to chaos. Cameras flashed. Murmurs rippled like waves through the crowd. Mr. JP, still standing on the stage beside his wife and son, narrowed his gaze.
The young lady, her face stained with tears and regret, dropped to her knees before James, her voice shaking but loud enough for everyone to hear.
“I’m sorry!” she cried. “Please forgive me… I… I was bribed! I was paid to come here and create a scene to disgrace you, to ruin your name”
James raised a brow, his face calm as stone.
The lady’s hand trembled as she pointed directly at two guests sitting stiffly in the second row. “It was them… Mark and Helen! They paid me. They told me to pretend I was your sister… I didn’t know it would go this far. I was desperate, and they offered me money!”
Gasps exploded in the room. Faces turned to Mark and Helen like a spotlight shifting focus. The weight of public scrutiny came crashing down.
“Lies!” Helen sprang up from her seat, her voice shrill and cracking. “She’s making it up! This is ridiculous! Why would I stoop so low?”
Mark stood next to her, adjusting his blazer as sweat gathered on his brow. “We’ve never seen this woman in our lives! She’s obviously been put up to this to frame us!”
James stepped forward, every inch the man now known as the true heir of JP Enterprises. “You both seem very quick to deny,” he said coolly, his gaze fixed like iron. “Are you implying this entire company, this crowd, and my family are foolish enough to believe a random accusation without evidence?”
“I’m saying this is staged,” Helen snapped, but her voice lacked its usual bite.
Before James could speak again, his uncle Charles walked toward the stage with a tablet in hand. “That’s interesting, because we already have transactional proof of your payments to her. Digital receipts. Surveillance footage. Voice recordings.” He held the tablet high. “Would you like me to play the part where you told her to make sure she cries in front of the cameras?”
The ballroom went utterly still.
Helen took a step back, her face paling. Mark's jaw clenched. “This… this can’t be real…”
“Oh, it’s very real,” James replied, his tone low and calm. “You thought you were playing chess while I was playing checkers. But I already saw the board long before you made your first move.”
Reporters surged forward, microphones extended, camera flashes dancing like strobe lights.
“Is this true, Mr. Mark? Ms. Helen?” “Were you behind the attempted defamation?” “Do you have any statement to make regarding the scandal?”
Helen was trembling now, her poise cracking under pressure. “You set us up!” she screamed. “You and your entire perfect little company, this is all a setup!”
“You did that yourself,” James said, his voice steady. “You tried to ruin me twice. Once in silence. Once in public. But the truth always finds light.”
Mr. JP raised his hand for silence. “I want them arrested,” he said firmly, turning to the uniformed security now entering the hall. “For defamation, for conspiracy, and for fraud.”
Helen turned to Mark. “Do something!”
Mark shook his head. “We’re finished…”
As the two were taken away by security, the entire room burst into conversations. Guests who had once smiled at Helen and Mark now recoiled. Their masks were gone. The truth was unveiled.
James turned to the young lady who was still kneeling. “You may go,” he said simply. “Justice isn’t yours to carry, it belongs to the law now.”
She nodded, tears falling anew, and left without a word.
Mrs. JP walked to her son’s side, taking his hand. “You’ve done well, James. Not just as a leader but as a man.”
Mr. JP smiled too, pride replacing the sternness in his eyes. “You’ve proven to this company and to this city that truth and integrity still win.”
James gave a slow nod, then stepped to the podium as the crowd turned toward him, waiting, hoping.
“I didn’t build JP Enterprises,” he said. “My father did. And many of you helped. But I will carry it forward. And I will protect it not just from failure, but from corruption.”
The ballroom quieted as James stepped down from the podium. The echoes of the applause still lingered like the gentle aftertaste of a vintage wine. People parted as he walked no longer the man whispered about in shadows, but the man now held in reverence. His walk was steady, composed. Every step was weighted with the dignity of a man who had not only reclaimed his name but risen far above the ones who tried to bury it.
Behind him, Helen and Mark were escorted out under the bright, unforgiving lights of press cameras and the judgment of a hundred curious eyes. There were no more veils to hide behind. No more pretense. Their downfall was no longer a quiet, whispered hope it was reality.
Outside the hall, as the night air kissed the courtyard, James stood with his mother, father, and Uncle Charles. Sandra and Rita joined them, both proud, both silent for a moment until Mrs. JP broke the silence.
-
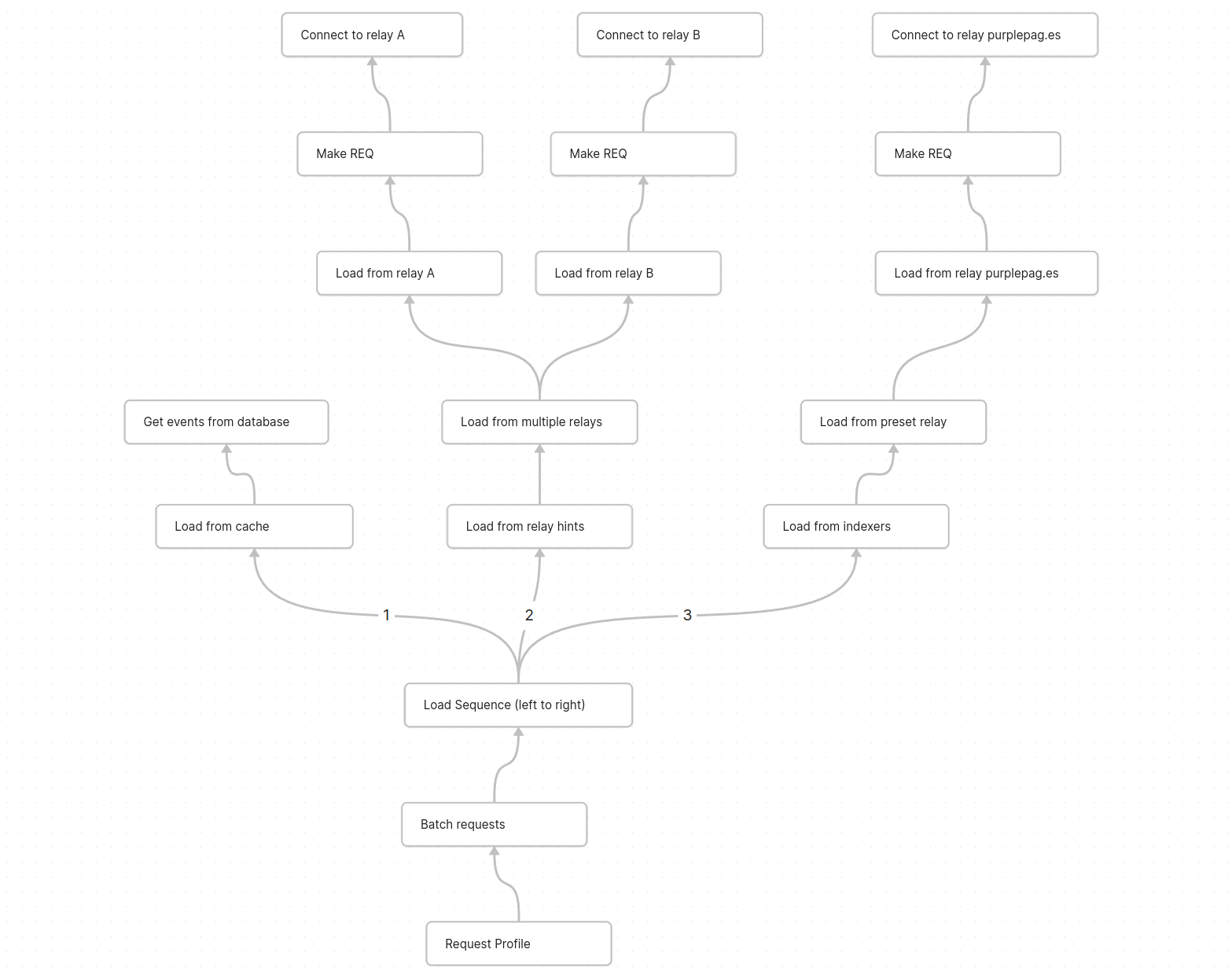
 @ 3bf0c63f:aefa459d
2024-03-19 15:35:35
@ 3bf0c63f:aefa459d
2024-03-19 15:35:35Nostr is not decentralized nor censorship-resistant
Peter Todd has been saying this for a long time and all the time I've been thinking he is misunderstanding everything, but I guess a more charitable interpretation is that he is right.
Nostr today is indeed centralized.
Yesterday I published two harmless notes with the exact same content at the same time. In two minutes the notes had a noticeable difference in responses:
The top one was published to
wss://nostr.wine,wss://nos.lol,wss://pyramid.fiatjaf.com. The second was published to the relay where I generally publish all my notes to,wss://pyramid.fiatjaf.com, and that is announced on my NIP-05 file and on my NIP-65 relay list.A few minutes later I published that screenshot again in two identical notes to the same sets of relays, asking if people understood the implications. The difference in quantity of responses can still be seen today:
These results are skewed now by the fact that the two notes got rebroadcasted to multiple relays after some time, but the fundamental point remains.
What happened was that a huge lot more of people saw the first note compared to the second, and if Nostr was really censorship-resistant that shouldn't have happened at all.
Some people implied in the comments, with an air of obviousness, that publishing the note to "more relays" should have predictably resulted in more replies, which, again, shouldn't be the case if Nostr is really censorship-resistant.
What happens is that most people who engaged with the note are following me, in the sense that they have instructed their clients to fetch my notes on their behalf and present them in the UI, and clients are failing to do that despite me making it clear in multiple ways that my notes are to be found on
wss://pyramid.fiatjaf.com.If we were talking not about me, but about some public figure that was being censored by the State and got banned (or shadowbanned) by the 3 biggest public relays, the sad reality would be that the person would immediately get his reach reduced to ~10% of what they had before. This is not at all unlike what happened to dozens of personalities that were banned from the corporate social media platforms and then moved to other platforms -- how many of their original followers switched to these other platforms? Probably some small percentage close to 10%. In that sense Nostr today is similar to what we had before.
Peter Todd is right that if the way Nostr works is that you just subscribe to a small set of relays and expect to get everything from them then it tends to get very centralized very fast, and this is the reality today.
Peter Todd is wrong that Nostr is inherently centralized or that it needs a protocol change to become what it has always purported to be. He is in fact wrong today, because what is written above is not valid for all clients of today, and if we drive in the right direction we can successfully make Peter Todd be more and more wrong as time passes, instead of the contrary.
See also:
-
 @ c631e267:c2b78d3e
2025-05-16 18:40:18
@ c631e267:c2b78d3e
2025-05-16 18:40:18Die zwei mächtigsten Krieger sind Geduld und Zeit. \ Leo Tolstoi
Zum Wohle unserer Gesundheit, unserer Leistungsfähigkeit und letztlich unseres Glücks ist es wichtig, die eigene Energie bewusst zu pflegen. Das gilt umso mehr für an gesellschaftlichen Themen interessierte, selbstbewusste und kritisch denkende Menschen. Denn für deren Wahrnehmung und Wohlbefinden waren und sind die rasanten, krisen- und propagandagefüllten letzten Jahre in Absurdistan eine harte Probe.
Nur wer regelmäßig Kraft tankt und Wege findet, mit den Herausforderungen umzugehen, kann eine solche Tortur überstehen, emotionale Erschöpfung vermeiden und trotz allem zufrieden sein. Dazu müssen wir erkunden, was uns Energie gibt und was sie uns raubt. Durch Selbstreflexion und Achtsamkeit finden wir sicher Dinge, die uns erfreuen und inspirieren, und andere, die uns eher stressen und belasten.
Die eigene Energie ist eng mit unserer körperlichen und mentalen Gesundheit verbunden. Methoden zur Förderung der körperlichen Gesundheit sind gut bekannt: eine ausgewogene Ernährung, regelmäßige Bewegung sowie ausreichend Schlaf und Erholung. Bei der nicht minder wichtigen emotionalen Balance wird es schon etwas komplizierter. Stress abzubauen, die eigenen Grenzen zu kennen oder solche zum Schutz zu setzen sowie die Konzentration auf Positives und Sinnvolles wären Ansätze.
Der emotionale ist auch der Bereich, über den «Energie-Räuber» bevorzugt attackieren. Das sind zum Beispiel Dinge wie Überforderung, Perfektionismus oder mangelhafte Kommunikation. Social Media gehören ganz sicher auch dazu. Sie stehlen uns nicht nur Zeit, sondern sind höchst manipulativ und erhöhen laut einer aktuellen Studie das Risiko für psychische Probleme wie Angstzustände und Depressionen.
Geben wir negativen oder gar bösen Menschen keine Macht über uns. Das Dauerfeuer der letzten Jahre mit Krisen, Konflikten und Gefahren sollte man zwar kennen, darf sich aber davon nicht runterziehen lassen. Das Ziel derartiger konzertierter Aktionen ist vor allem, unsere innere Stabilität zu zerstören, denn dann sind wir leichter zu steuern. Aber Geduld: Selbst vermeintliche «Sonnenköniginnen» wie EU-Kommissionspräsidentin von der Leyen fallen, wenn die Zeit reif ist.
Es ist wichtig, dass wir unsere ganz eigenen Bedürfnisse und Werte erkennen. Unsere Energiequellen müssen wir identifizieren und aktiv nutzen. Dazu gehören soziale Kontakte genauso wie zum Beispiel Hobbys und Leidenschaften. Umgeben wir uns mit Sinnhaftigkeit und lassen wir uns nicht die Energie rauben!
Mein Wahlspruch ist schon lange: «Was die Menschen wirklich bewegt, ist die Kultur.» Jetzt im Frühjahr beginnt hier in Andalusien die Zeit der «Ferias», jener traditionellen Volksfeste, die vor Lebensfreude sprudeln. Konzentrieren wir uns auf die schönen Dinge und auf unsere eigenen Talente – soziale Verbundenheit wird helfen, unsere innere Kraft zu stärken und zu bewahren.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 58537364:705b4b85
2025-05-17 06:31:52
@ 58537364:705b4b85
2025-05-17 06:31:52ความสำเร็จ จำเป็นต้องมีวินัย
ความมีวินัย คือ "การทำด้วยความตั้งใจ ไม่หวั่นไหว/ไหลตามไปกับอารมณ์" ส่วน "ความไร้วินัย" มีนัยยะตรงกันข้าม กล่าวคือ
ความไร้วินัย คือ "การทำตามความหวั่นไหว/ไหลตามไปกับอารมณ์" เช่น ความง่วง หิว เบื่อ เซ็ง พอใจ ไม่พอใจ กลัว หลงไหล/ขาดสติ เป็นต้น จนเกิดข้ออ้างสารพัด เช่น * อ้างว่าเดี๋ยวก่อน เอาไว้ทีหลัง * อ้างว่าเหนื่อยหน่าย * อ้างว่าร้อนไป หนาวไป * อ้างว่ายังเช้าอยู่ * อ้างว่าสายไปแล้ว * ฯลฯ
การสร้างวินัยที่ยั่งยืน "ไม่ได้เกิดจากการฝืน แต่เกิดจากความฝัน" กฎแห่งความฝันระบุว่า เราต้องสร้างภาพสวรรค์ (เป้าหมาย) ให้ชัด จากนั้นให้ลดช่องว่างระหว่างการคิดและการกระทำให้เหลือน้อยที่สุด เพราะถ้าเราคิดมาก ส่วนใหญ่เราจะไม่ได้ทำ จิตใจเราจะอ่อนแอ ไม่เข้มแข็งมั่นคง
กฎแห่งความฝัน ควรฝันเพื่อผู้อื่น อย่าฝันเพื่อตัวเองคนเดียว เพราะขณะที่จิตมุ่งเป้าสู่ความสำเร็จนั้นมัน ถ้ามันมีมากเกินไป สติปัญญาจะอ่อนค่าลง ความรอบรู้จะน้อยลง ณ ขณะนั้นการกระทำทั้งปวงจะขาดความเห็นอกเห็นใจผู้อื่นหากทำเพื่อตัวเองฝ่ายเดียว แต่ถ้าพลังมุ่งเป้าที่ส่วนรวม ทุกการกระทำจะส่งคุณค่าเกิดเป็นความสุขความสำเร็จร่วมกัน
-เมธา หริมเทพาธิบดี
คู่มือมนุษย์
-
 @ 3bf0c63f:aefa459d
2024-03-19 13:07:02
@ 3bf0c63f:aefa459d
2024-03-19 13:07:02Censorship-resistant relay discovery in Nostr
In Nostr is not decentralized nor censorship-resistant I said Nostr is centralized. Peter Todd thinks it is centralized by design, but I disagree.
Nostr wasn't designed to be centralized. The idea was always that clients would follow people in the relays they decided to publish to, even if it was a single-user relay hosted in an island in the middle of the Pacific ocean.
But the Nostr explanations never had any guidance about how to do this, and the protocol itself never had any enforcement mechanisms for any of this (because it would be impossible).
My original idea was that clients would use some undefined combination of relay hints in reply tags and the (now defunct)
kind:2relay-recommendation events plus some form of manual action ("it looks like Bob is publishing on relay X, do you want to follow him there?") to accomplish this. With the expectation that we would have a better idea of how to properly implement all this with more experience, Branle, my first working client didn't have any of that implemented, instead it used a stupid static list of relays with read/write toggle -- although it did publish relay hints and kept track of those internally and supportedkind:2events, these things were not really useful.Gossip was the first client to implement a truly censorship-resistant relay discovery mechanism that used NIP-05 hints (originally proposed by Mike Dilger) relay hints and
kind:3relay lists, and then with the simple insight of NIP-65 that got much better. After seeing it in more concrete terms, it became simpler to reason about it and the approach got popularized as the "gossip model", then implemented in clients like Coracle and Snort.Today when people mention the "gossip model" (or "outbox model") they simply think about NIP-65 though. Which I think is ok, but too restrictive. I still think there is a place for the NIP-05 hints,
nprofileandneventrelay hints and specially relay hints in event tags. All these mechanisms are used together in ZBD Social, for example, but I believe also in the clients listed above.I don't think we should stop here, though. I think there are other ways, perhaps drastically different ways, to approach content propagation and relay discovery. I think manual action by users is underrated and could go a long way if presented in a nice UX (not conceived by people that think users are dumb animals), and who knows what. Reliance on third-parties, hardcoded values, social graph, and specially a mix of multiple approaches, is what Nostr needs to be censorship-resistant and what I hope to see in the future.
-
 @ 04c915da:3dfbecc9
2025-05-16 18:06:46
@ 04c915da:3dfbecc9
2025-05-16 18:06:46Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Using stolen bitcoin for the reserve creates a perverse incentive. If governments see bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 3bf0c63f:aefa459d
2024-01-29 02:19:25
@ 3bf0c63f:aefa459d
2024-01-29 02:19:25Nostr: a quick introduction, attempt #1
Nostr doesn't have a material existence, it is not a website or an app. Nostr is just a description what kind of messages each computer can send to the others and vice-versa. It's a very simple thing, but the fact that such description exists allows different apps to connect to different servers automatically, without people having to talk behind the scenes or sign contracts or anything like that.
When you use a Nostr client that is what happens, your client will connect to a bunch of servers, called relays, and all these relays will speak the same "language" so your client will be able to publish notes to them all and also download notes from other people.
That's basically what Nostr is: this communication layer between the client you run on your phone or desktop computer and the relay that someone else is running on some server somewhere. There is no central authority dictating who can connect to whom or even anyone who knows for sure where each note is stored.
If you think about it, Nostr is very much like the internet itself: there are millions of websites out there, and basically anyone can run a new one, and there are websites that allow you to store and publish your stuff on them.
The added benefit of Nostr is that this unified "language" that all Nostr clients speak allow them to switch very easily and cleanly between relays. So if one relay decides to ban someone that person can switch to publishing to others relays and their audience will quickly follow them there. Likewise, it becomes much easier for relays to impose any restrictions they want on their users: no relay has to uphold a moral ground of "absolute free speech": each relay can decide to delete notes or ban users for no reason, or even only store notes from a preselected set of people and no one will be entitled to complain about that.
There are some bad things about this design: on Nostr there are no guarantees that relays will have the notes you want to read or that they will store the notes you're sending to them. We can't just assume all relays will have everything — much to the contrary, as Nostr grows more relays will exist and people will tend to publishing to a small set of all the relays, so depending on the decisions each client takes when publishing and when fetching notes, users may see a different set of replies to a note, for example, and be confused.
Another problem with the idea of publishing to multiple servers is that they may be run by all sorts of malicious people that may edit your notes. Since no one wants to see garbage published under their name, Nostr fixes that by requiring notes to have a cryptographic signature. This signature is attached to the note and verified by everybody at all times, which ensures the notes weren't tampered (if any part of the note is changed even by a single character that would cause the signature to become invalid and then the note would be dropped). The fix is perfect, except for the fact that it introduces the requirement that each user must now hold this 63-character code that starts with "nsec1", which they must not reveal to anyone. Although annoying, this requirement brings another benefit: that users can automatically have the same identity in many different contexts and even use their Nostr identity to login to non-Nostr websites easily without having to rely on any third-party.
To conclude: Nostr is like the internet (or the internet of some decades ago): a little chaotic, but very open. It is better than the internet because it is structured and actions can be automated, but, like in the internet itself, nothing is guaranteed to work at all times and users many have to do some manual work from time to time to fix things. Plus, there is the cryptographic key stuff, which is painful, but cool.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:59:23
@ 04c915da:3dfbecc9
2025-05-16 17:59:23Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ 3b62c542:6f45deaf
2025-05-17 05:14:41
@ 3b62c542:6f45deaf
2025-05-17 05:14:41The cryptocurrency landscape, once dominated by wild price swings and volatile tokens like Bitcoin and Ethereum, is witnessing a quiet but seismic shift. Stablecoins cryptocurrencies pegged to traditional assets like the U.S. dollar are increasingly taking center stage. While not as flashy as their high-flying cousins, stablecoins are proving to be the most functional and widely adopted segment of the crypto universe. Simply put: stablecoins are eating crypto.
What are stablecoins?
Stablecoins are digital assets designed to maintain a stable value relative to a fiat currency or commodity. The most popular stablecoins, such as Tether (USDT), USD Coin (USDC), and DAI, are typically pegged 1:1 to the U.S. dollar. Their stability makes them ideal for transactions, trading, and storing value, especially in the notoriously volatile crypto markets.
There are three main types of stablecoins:
- Fiat-collateralized: Backed by reserves of fiat currencies held in bank accounts.
- Crypto-collateralized: Backed by other cryptocurrencies, usually overcollateralized to handle volatility.
- Algorithmic: Maintain their peg through supply-and-demand algorithms without actual reserves (e.g., the failed TerraUSD).
The rise in utility
What started as a tool for traders to hedge volatility has become the backbone of decentralized finance (DeFi), cross-border remittances, and even some central bank strategies. Stablecoins now play multiple roles:
- Medium of exchange: Unlike Bitcoin, which is rarely used in daily transactions due to its fluctuating price, stablecoins are ideal for payments.
- Liquidity providers: In DeFi, stablecoins serve as the base currency for lending, borrowing, and yield farming.
- Trading pairs: A large percentage of crypto trading volume is denominated in stablecoins, not in Bitcoin or fiat.
Growing market share
As of mid-2025, stablecoins represent a multi-hundred-billion-dollar market. Tether remains the largest by market cap, followed by USDC. Their total volume now rivals or in some days, exceeds that of Bitcoin and Ethereum. According to data from multiple crypto analytics platforms, stablecoins accounted for more than 70% of on-chain transaction volume in early 2025, highlighting their dominance in practical use cases.
Central banks and regulation
Stablecoins are also reshaping conversations around monetary sovereignty. Central banks are watching closely, with some developing their own Central Bank Digital Currencies (CBDCs) to compete. Meanwhile, regulators are scrambling to craft frameworks to oversee stablecoin issuers, particularly around reserve transparency and systemic risk.
The U.S. and EU are working toward legislation requiring stablecoin issuers to hold audited 1:1 reserves and submit to regular oversight, essentially treating them like narrow banks. The goal: harness the efficiency of stablecoins without compromising financial stability.
Why stablecoins are winning
- Trust and predictability: In crypto, stability is a feature, not a bug. Traders and users prefer assets they can rely on for everyday transactions.
- Interoperability: Stablecoins are blockchain-agnostic and can be used across multiple networks like Ethereum, Solana, and Polygon.
- Programmability: They bring the efficiency of smart contracts to money itself, enabling automated, low-cost transactions.
- Global access: Stablecoins offer dollar exposure to users in countries with unstable local currencies, providing financial inclusion with just a smartphone.
The ironic future
Ironically, the original vision of cryptocurrencies decentralized, uncensorable money has been somewhat sidelined by stablecoins, which often rely on centralized issuers and custodians. The dream of Bitcoin as digital cash is being fulfilled not by Bitcoin itself, but by stablecoins. That paradox lies at the heart of stablecoins’ quiet conquest.
Conclusion
Stablecoins may not grab headlines like Bitcoin bull runs or Ethereum upgrades, but their steady, practical growth is transforming crypto from a speculative playground into a functional financial ecosystem. As regulation crystallizes and usage continues to rise, stablecoins are not just part of the crypto industry they're becoming its foundation. And in doing so, they're slowly but surely eating the rest of crypto alive.
-
 @ 3bf0c63f:aefa459d
2024-01-15 11:15:06
@ 3bf0c63f:aefa459d
2024-01-15 11:15:06Pequenos problemas que o Estado cria para a sociedade e que não são sempre lembrados
- **vale-transporte**: transferir o custo com o transporte do funcionário para um terceiro o estimula a morar longe de onde trabalha, já que morar perto é normalmente mais caro e a economia com transporte é inexistente. - **atestado médico**: o direito a faltar o trabalho com atestado médico cria a exigência desse atestado para todas as situações, substituindo o livre acordo entre patrão e empregado e sobrecarregando os médicos e postos de saúde com visitas desnecessárias de assalariados resfriados. - **prisões**: com dinheiro mal-administrado, burocracia e péssima alocação de recursos -- problemas que empresas privadas em competição (ou mesmo sem qualquer competição) saberiam resolver muito melhor -- o Estado fica sem presídios, com os poucos existentes entupidos, muito acima de sua alocação máxima, e com isto, segundo a bizarra corrente de responsabilidades que culpa o juiz que condenou o criminoso por sua morte na cadeia, juízes deixam de condenar à prisão os bandidos, soltando-os na rua. - **justiça**: entrar com processos é grátis e isto faz proliferar a atividade dos advogados que se dedicam a criar problemas judiciais onde não seria necessário e a entupir os tribunais, impedindo-os de fazer o que mais deveriam fazer. - **justiça**: como a justiça só obedece às leis e ignora acordos pessoais, escritos ou não, as pessoas não fazem acordos, recorrem sempre à justiça estatal, e entopem-na de assuntos que seriam muito melhor resolvidos entre vizinhos. - **leis civis**: as leis criadas pelos parlamentares ignoram os costumes da sociedade e são um incentivo a que as pessoas não respeitem nem criem normas sociais -- que seriam maneiras mais rápidas, baratas e satisfatórias de resolver problemas. - **leis de trãnsito**: quanto mais leis de trânsito, mais serviço de fiscalização são delegados aos policiais, que deixam de combater crimes por isto (afinal de contas, eles não querem de fato arriscar suas vidas combatendo o crime, a fiscalização é uma excelente desculpa para se esquivarem a esta responsabilidade). - **financiamento educacional**: é uma espécie de subsídio às faculdades privadas que faz com que se criem cursos e mais cursos que são cada vez menos recheados de algum conhecimento ou técnica útil e cada vez mais inúteis. - **leis de tombamento**: são um incentivo a que o dono de qualquer área ou construção "histórica" destrua todo e qualquer vestígio de história que houver nele antes que as autoridades descubram, o que poderia não acontecer se ele pudesse, por exemplo, usar, mostrar e se beneficiar da história daquele local sem correr o risco de perder, de fato, a sua propriedade. - **zoneamento urbano**: torna as cidades mais espalhadas, criando uma necessidade gigantesca de carros, ônibus e outros meios de transporte para as pessoas se locomoverem das zonas de moradia para as zonas de trabalho. - **zoneamento urbano**: faz com que as pessoas percam horas no trânsito todos os dias, o que é, além de um desperdício, um atentado contra a sua saúde, que estaria muito melhor servida numa caminhada diária entre a casa e o trabalho. - **zoneamento urbano**: torna ruas e as casas menos seguras criando zonas enormes, tanto de residências quanto de indústrias, onde não há movimento de gente alguma. - **escola obrigatória + currículo escolar nacional**: emburrece todas as crianças. - **leis contra trabalho infantil**: tira das crianças a oportunidade de aprender ofícios úteis e levar um dinheiro para ajudar a família. - **licitações**: como não existem os critérios do mercado para decidir qual é o melhor prestador de serviço, criam-se comissões de pessoas que vão decidir coisas. isto incentiva os prestadores de serviço que estão concorrendo na licitação a tentar comprar os membros dessas comissões. isto, fora a corrupção, gera problemas reais: __(i)__ a escolha dos serviços acaba sendo a pior possível, já que a empresa prestadora que vence está claramente mais dedicada a comprar comissões do que a fazer um bom trabalho (este problema afeta tantas áreas, desde a construção de estradas até a qualidade da merenda escolar, que é impossível listar aqui); __(ii)__ o processo corruptor acaba, no longo prazo, eliminando as empresas que prestavam e deixando para competir apenas as corruptas, e a qualidade tende a piorar progressivamente. - **cartéis**: o Estado em geral cria e depois fica refém de vários grupos de interesse. o caso dos taxistas contra o Uber é o que está na moda hoje (e o que mostra como os Estados se comportam da mesma forma no mundo todo). - **multas**: quando algum indivíduo ou empresa comete uma fraude financeira, ou causa algum dano material involuntário, as vítimas do caso são as pessoas que sofreram o dano ou perderam dinheiro, mas o Estado tem sempre leis que prevêem multas para os responsáveis. A justiça estatal é sempre muito rígida e rápida na aplicação dessas multas, mas relapsa e vaga no que diz respeito à indenização das vítimas. O que em geral acontece é que o Estado aplica uma enorme multa ao responsável pelo mal, retirando deste os recursos que dispunha para indenizar as vítimas, e se retira do caso, deixando estas desamparadas. - **desapropriação**: o Estado pode pegar qualquer propriedade de qualquer pessoa mediante uma indenização que é necessariamente inferior ao valor da propriedade para o seu presente dono (caso contrário ele a teria vendido voluntariamente). - **seguro-desemprego**: se há, por exemplo, um prazo mínimo de 1 ano para o sujeito ter direito a receber seguro-desemprego, isto o incentiva a planejar ficar apenas 1 ano em cada emprego (ano este que será sucedido por um período de desemprego remunerado), matando todas as possibilidades de aprendizado ou aquisição de experiência naquela empresa específica ou ascensão hierárquica. - **previdência**: a previdência social tem todos os defeitos de cálculo do mundo, e não importa muito ela ser uma forma horrível de poupar dinheiro, porque ela tem garantias bizarras de longevidade fornecidas pelo Estado, além de ser compulsória. Isso serve para criar no imaginário geral a idéia da __aposentadoria__, uma época mágica em que todos os dias serão finais de semana. A idéia da aposentadoria influencia o sujeito a não se preocupar em ter um emprego que faça sentido, mas sim em ter um trabalho qualquer, que o permita se aposentar. - **regulamentação impossível**: milhares de coisas são proibidas, há regulamentações sobre os aspectos mais mínimos de cada empreendimento ou construção ou espaço. se todas essas regulamentações fossem exigidas não haveria condições de produção e todos morreriam. portanto, elas não são exigidas. porém, o Estado, ou um agente individual imbuído do poder estatal pode, se desejar, exigi-las todas de um cidadão inimigo seu. qualquer pessoa pode viver a vida inteira sem cumprir nem 10% das regulamentações estatais, mas viverá também todo esse tempo com medo de se tornar um alvo de sua exigência, num estado de terror psicológico. - **perversão de critérios**: para muitas coisas sobre as quais a sociedade normalmente chegaria a um valor ou comportamento "razoável" espontaneamente, o Estado dita regras. estas regras muitas vezes não são obrigatórias, são mais "sugestões" ou limites, como o salário mínimo, ou as 44 horas semanais de trabalho. a sociedade, porém, passa a usar esses valores como se fossem o normal. são raras, por exemplo, as ofertas de emprego que fogem à regra das 44h semanais. - **inflação**: subir os preços é difícil e constrangedor para as empresas, pedir aumento de salário é difícil e constrangedor para o funcionário. a inflação força as pessoas a fazer isso, mas o aumento não é automático, como alguns economistas podem pensar (enquanto alguns outros ficam muito satisfeitos de que esse processo seja demorado e difícil). - **inflação**: a inflação destrói a capacidade das pessoas de julgar preços entre concorrentes usando a própria memória. - **inflação**: a inflação destrói os cálculos de lucro/prejuízo das empresas e prejudica enormemente as decisões empresariais que seriam baseadas neles. - **inflação**: a inflação redistribui a riqueza dos mais pobres e mais afastados do sistema financeiro para os mais ricos, os bancos e as megaempresas. - **inflação**: a inflação estimula o endividamento e o consumismo. - **lixo:** ao prover coleta e armazenamento de lixo "grátis para todos" o Estado incentiva a criação de lixo. se tivessem que pagar para que recolhessem o seu lixo, as pessoas (e conseqüentemente as empresas) se empenhariam mais em produzir coisas usando menos plástico, menos embalagens, menos sacolas. - **leis contra crimes financeiros:** ao criar legislação para dificultar acesso ao sistema financeiro por parte de criminosos a dificuldade e os custos para acesso a esse mesmo sistema pelas pessoas de bem cresce absurdamente, levando a um percentual enorme de gente incapaz de usá-lo, para detrimento de todos -- e no final das contas os grandes criminosos ainda conseguem burlar tudo. -
 @ 502ab02a:a2860397
2025-05-17 03:21:54
@ 502ab02a:a2860397
2025-05-17 03:21:54ยังมีเรื่องราวของน้ำตาล และ เซลล์ มาคุยกันต่อนะครับ เพราะยังมีคนสงสัยอยู่ว่า เอ้ย ตกลงต้องห่วงการ Spike&Staylong ของอินซุลินอยู่หรือเปล่า แล้วถ้าเราไม่ spike&staylong ก็คือกินคาร์บเบาๆตลอดวันได้เลยใช่ไหมก็มันไม่ spike&staylong แล้วนี่ โอเคครับ เรามาเปิดผับกันอีกครั้ง
คราวก่อนนั้นเราคุยกันเรื่อง ผับน้ำตาลกันไปแล้วนะครับว่า เมื่ออินซูลิน spike สูง และค้างนาน เหมือนเปิดผับแล้ววัยรุ่นแห่กันเข้ามาเที่ยว จนพีอาร์เมาจัด
เผื่อใครจำไม่ได้ ย้อนให้นิดๆครับ ว่าให้ลองนึกภาพว่าเฮียเปิดผับอยู่ดี ๆ ลูกค้าหลั่งไหลเข้ามารัว ๆ เหมือนมีโปรเบียร์ 1 แถม 10 ตอนสามทุ่ม ทุกโต๊ะสั่งข้าวเหนียวหมูปิ้งพร้อมเบียร์น้ำแข็งเต็มโต๊ะ นักเที่ยวก็ยังแห่เข้าผับแบบไม่มีพัก อินซูลินซึ่งเป็นเหมือน “พีอาร์” ที่ต้องจัดการรับแขก (หรือรับน้ำตาลเข้าสู่เซลล์) ก็เลยต้องทำงานหนักแบบ non-stop
อินซูลินเป็นฮอร์โมนสำคัญที่ช่วยเอาน้ำตาลในเลือดเข้าไปเก็บในเซลล์ ถ้า spike ทีเดียวสูงมาก เซลล์ก็รีบดูดน้ำตาลเข้าไปเต็มที่จนเกินพิกัด เหมือนผับที่แน่นจนปิดประตูไม่ลง
ถ้าเหตุการณ์แบบนี้เกิดขึ้นบ่อย ๆ ร่างกายจะเริ่มรู้สึกว่า “ทำไมอินซูลินถึงต้องออกมาบ่อยขนาดนี้วะ?” ระบบก็เริ่มปิดรับแขก เซลล์เริ่มไม่อยากตอบสนอง เพราะมันเหนื่อย มันชิน และมันก็เริ่ม “ดื้ออินซูลิน”
ผลที่ตามมาเมื่อ spike สูงและค้าง สิ่งที่ตามมา... คือความปั่นป่วนในร่างกายอย่างต่อเนื่อง น้ำตาลลอยค้างในเลือด ไปจับกับโปรตีนจนกลายเป็นเจ้า AGEs ตัวร้าย ไขมันก็ถูกสร้างมากขึ้น ล้นเข้าไปสะสมในตับ ในพุง ในซอกที่ร่างกายไม่รู้จะเก็บไว้ตรงไหนแล้ว สมองก็เบลอ ใจวูบ ง่วงงุน... เหมือนเข้าเวรประชุมยาวแบบไม่มีกาแฟ ฮอร์โมนที่เคยเป็นทีมงานสามัคคี ก็เริ่มทะเลาะกันเอง อินซูลินงอน leptin งง ghrelin งวย
แล้วถ้าเราไม่ spike แต่กินคาร์บจุ๋มจิ๋มทั้งวันล่ะ? พอรู้ว่าการเปิดผับแจกคาร์บแบบจัดหนักไม่ดี หลายคนก็ปรับกลยุทธ์ใหม่ มาแนวสายสุขุมว่า “งั้นเปิดผับแบบเนิบ ๆ ก็แล้วกัน… ไม่จัดปาร์ตี้ใหญ่ แต่มีแขกแวะเข้ามาทั้งวัน” ฟังดูดีใช่ไหม? แต่เอาเข้าจริง มันเหนื่อยไม่แพ้กันเลย
ลองนึกภาพว่าประเทศไม่มีเคอร์ฟิว เฮียเปิดผับที่มีลูกค้าเดินเข้าออกไม่หยุด ไม่ได้มากันเป็นฝูงแบบรอบโปรโมชั่น แต่มาเรื่อย ๆ แบบชั่วโมงละโต๊ะ สองโต๊ะ พีอาร์ อินซูลิน ก็เลยต้องยืนต้อนรับแขกตลอดเวลา ไม่มีเวลานั่งพัก ไม่มีช่วงเปลี่ยนกะ ไม่มีเวลาปิดไฟเก็บโต๊ะ คือทำงานต่อเนื่องยาว ๆ ตั้งแต่ 8 โมงเช้า ยัน 8 โมงเช้า สุดท้าย ผับก็เปิดไฟยันสว่าง อินซูลินก็กลายเป็นพนักงานกะดึกตลอดชีพ และเมื่อไม่มีเวลา “พักผับ” ระบบหลังบ้านก็ไม่เคยได้ฟื้นฟูเลย
ภาพรวมของการกินจุ๋มจิ๋มทั้งวันแบบนี้นั้น - เผาผลาญไขมันไม่ออกเลย เพราะอินซูลินทำหน้าที่เหมือนไฟบนเวที ถ้ายังเปิดไฟอยู่ “เครื่องดูดไขมันหลังร้าน” มันก็ไม่ทำงาน - แม่บ้านทำความสะอาดก็เข้าไม่ได้ เพราะแขกเดินเข้าเดินออกตลอด ระบบกำจัดที่ควรจะได้ล้างของเสียในเซลล์ ก็เลยโดนขัดจังหวะตลอด - พนักงานเหนื่อยสะสมจากงานไม่มีหยุด ทำให้เกิดความเครียดสะสมในร่างกาย ฮอร์โมนรวน อารมณ์ก็แปรปรวนง่ายขึ้น หิวเก่งขึ้น ทั้งที่เพิ่งกินไป
เปิดผับแบบคึกคักจัดเต็มทีเดียว แล้วปิดยาว หรือ เปิดทั้งวันแบบไม่มีช่วงปิด สุดท้ายพังทั้งคู่
ทีนี้เราน่าจะพอเห็นภาพร่างคร่าวๆ ของการบริหารการจัดการน้ำตาลในตัวเราได้แล้วนะครับ ว่าจะไดเอทไหนก็ตาม การบริหารการจัดการฮอร์โมนส์ คือสิ่งสำคัญไม่แพ้เรื่องอื่นๆ แม้จะไม่ใช่เรื่องสำคัญที่สุดในสายตาใครก็ตาม
นี่เป็นเพียงจุดเริ่มต้นการเรียนรู้เล็กๆ ซึ่งเส้นทางสายที่เรียกว่า ร่างกาย มันยังไปไกลอีกลิบลับเลยครับ ไม่ว่าจะจังหวัดคอติซอล จังหวัดพฤกษเคมี จังหวัดพลังงาน จังหวัดสารอาหาร แถมลักษณะร่างกายแต่ละคน ก็เปรียบเหมือนรถต่างยี่ห้อ ต่างน้ำมันขับเคลื่อน ต่างซีซี หรือแม้ว่าจะเหมือนกัน ก็ยังต่างปี ต่างไมล์การขับขี่
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ c9badfea:610f861a
2025-05-17 03:08:55
@ c9badfea:610f861a
2025-05-17 03:08:55- Install Rethink (it's free and open source)
- Launch the app and tap Skip
- Tap Start and then Proceed to set up the VPN connection
- Allow notifications and Proceed, then disable battery optimization for this app (you may need to set it to Unrestricted)
- Navigate to Configure and tap Apps
- On the top bar, tap 🛜 and 📶 to block all apps from connecting to the internet
- Search Apps for the apps you want to allow and Bypass Universal
- Return to the Configure view and tap DNS, then choose your preferred DNS provider (e.g. DNSCrypt > Quad9)
- Optionally, tap On-Device Blocklists, then Disabled, Download Blocklists, and later Configure (you may need to enable the Use In-App Downloader option if the download is not working)
- Return to the Configure view and tap Firewall, then Universal Firewall Rules and enable the options as desired:
- Block all apps when device is locked
- Block newly installed apps by default
- Block when DNS is bypassed
- Optionally, to set up WireGuard or Tor, return to the Configure view and tap Proxy
- For Tor, tap Setup Orbot, then optionally select all the apps that should route through Tor (you must have Orbot installed)
- For WireGuard, tap Setup WireGuard, then +, and select an option to import a WireGuard configuration (QR Code Scan, File Import, or Creation).
- Use Simple Mode for a single WireGuard connection (all apps are routed through it).
- Use Advanced Mode for multiple WireGuard connections (split tunnel, manually choosing apps to route through them)
⚠️ Use this app only if you know what you are doing, as misconfiguration can lead to missing notifications and other problems
ℹ️ On the main view, tap Logs to track all connections
ℹ️ You can also use a WireGuard connection (e.g., from your VPN provider) and on-device blocklists together
-
 @ 04c915da:3dfbecc9
2025-05-16 17:51:54
@ 04c915da:3dfbecc9
2025-05-16 17:51:54In much of the world, it is incredibly difficult to access U.S. dollars. Local currencies are often poorly managed and riddled with corruption. Billions of people demand a more reliable alternative. While the dollar has its own issues of corruption and mismanagement, it is widely regarded as superior to the fiat currencies it competes with globally. As a result, Tether has found massive success providing low cost, low friction access to dollars. Tether claims 400 million total users, is on track to add 200 million more this year, processes 8.1 million transactions daily, and facilitates $29 billion in daily transfers. Furthermore, their estimates suggest nearly 40% of users rely on it as a savings tool rather than just a transactional currency.
Tether’s rise has made the company a financial juggernaut. Last year alone, Tether raked in over $13 billion in profit, with a lean team of less than 100 employees. Their business model is elegantly simple: hold U.S. Treasuries and collect the interest. With over $113 billion in Treasuries, Tether has turned a straightforward concept into a profit machine.
Tether’s success has resulted in many competitors eager to claim a piece of the pie. This has triggered a massive venture capital grift cycle in USD tokens, with countless projects vying to dethrone Tether. Due to Tether’s entrenched network effect, these challengers face an uphill battle with little realistic chance of success. Most educated participants in the space likely recognize this reality but seem content to perpetuate the grift, hoping to cash out by dumping their equity positions on unsuspecting buyers before they realize the reality of the situation.
Historically, Tether’s greatest vulnerability has been U.S. government intervention. For over a decade, the company operated offshore with few allies in the U.S. establishment, making it a major target for regulatory action. That dynamic has shifted recently and Tether has seized the opportunity. By actively courting U.S. government support, Tether has fortified their position. This strategic move will likely cement their status as the dominant USD token for years to come.
While undeniably a great tool for the millions of users that rely on it, Tether is not without flaws. As a centralized, trusted third party, it holds the power to freeze or seize funds at its discretion. Corporate mismanagement or deliberate malpractice could also lead to massive losses at scale. In their goal of mitigating regulatory risk, Tether has deepened ties with law enforcement, mirroring some of the concerns of potential central bank digital currencies. In practice, Tether operates as a corporate CBDC alternative, collaborating with authorities to surveil and seize funds. The company proudly touts partnerships with leading surveillance firms and its own data reveals cooperation in over 1,000 law enforcement cases, with more than $2.5 billion in funds frozen.
The global demand for Tether is undeniable and the company’s profitability reflects its unrivaled success. Tether is owned and operated by bitcoiners and will likely continue to push forward strategic goals that help the movement as a whole. Recent efforts to mitigate the threat of U.S. government enforcement will likely solidify their network effect and stifle meaningful adoption of rival USD tokens or CBDCs. Yet, for all their achievements, Tether is simply a worse form of money than bitcoin. Tether requires trust in a centralized entity, while bitcoin can be saved or spent without permission. Furthermore, Tether is tied to the value of the US Dollar which is designed to lose purchasing power over time, while bitcoin, as a truly scarce asset, is designed to increase in purchasing power with adoption. As people awaken to the risks of Tether’s control, and the benefits bitcoin provides, bitcoin adoption will likely surpass it.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:12:05
@ 04c915da:3dfbecc9
2025-05-16 17:12:05One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 57d1a264:69f1fee1
2025-05-16 07:51:08
@ 57d1a264:69f1fee1
2025-05-16 07:51:08Payjoin allows the sender and receiver of an on-chain payment to collaborate and create a transaction that breaks on-chain heuristics, allowing a more private transaction with ambiguous payment amount and UTXO ownership. Additionally, it can also be used for UTXO consolidation (receiver saves future fees) and batching payments (receiver can make payment(s) of their own in the process of receiving one), also known as transaction cut-through. Other than improved privacy, the rest of the benefits are typically applicable to the receiver, not the sender.
BIP-78 was the original payjoin protocol that required the receiver to run a endpoint/server (always online) in order to mediate the payjoin process. Payjoin adoption has remained pretty low, something attributed to the server & perpetual online-ness requirement. This is the motivation for payjoin v2.
The purpose of the one-pager is to analyse the protocol, and highlight the UX issues or tradeoffs it entails, so that the payjoin user flows can be appropriately designed and the tradeoffs likewise communicated. A further document on UX solutions might be needed to identify solutions and opportunities
The following observations are generally limited to individual users transacting through their mobile devices:
While users naturally want better privacy and fee-savings, they also want to minimise friction and minimise (optimise) payment time. These are universal and more immediate needs since they deal with the user experience.
Added manual steps
TL;DR v2 payjoin eliminates server & simultaneous user-liveness requirements (increasing TAM, and opportunities to payjoin, as a result) by adding manual steps.
Usually, the extent of the receiver's involvement in the transaction process is limited to sharing their address with the sender. Once they share the address/URI, they can basically forget about it. In the target scenario for v2 payjoin, the receiver must come online again (except they have no way of knowing "when") to contribute input(s) and sign the PSBT. This can be unexpected, unintuitive and a bit of a hassle.
Usually (and even with payjoin v1), the sender crafts and broadcasts the transaction in one go; meaning the user's job is done within a few seconds/minutes. With payjoin v2, they must share the original-PSBT with the receiver, and then wait for them to do their part. Once the the receiver has done that, the sender must come online to review the transaction, sign it & broadcast.
In summary,
In payjoin v1, step 3 is automated and instant, so delay 2, 3 =~ 0. As the user experiences it, the process is completed in a single session, akin to a non-payjoin transaction.
With payjoin v2, Steps 2 & 3 in the above diagram are widely spread and noticeable. These manual steps are separated by uncertain delays (more on that below) when compared to a non-payjoin transaction.
Delays
We've established that both senders and receivers must take extra manual steps to execute a payoin transaction. With payjoin v2, this process gets split into multiple sessions, since the sender and receiver are not like to be online simultaneously.
Delay 2 & 3 (see diagram above) are uncertain in nature. Most users do not open their bitcoin wallets for days or weeks! The receiver must come online before the timeout hits in order for the payjoin process to work, otherwise time is just wasted with no benefit. UX or technical solutions are needed to minimise these delays.
Delays might be exacerbated if the setup is based on hardware wallet and/or uses multisig.
Notifications or background processes
There is one major problem when we say "the user must come online to..." but in reality the user has no way of knowing there is a payjoin PSBT waiting for them. After a PSBT is sent to the relay, the opposite user would only find out about it whenever they happen to come online. Notifications and background sync processes might be necessary to minimise delays. This is absolutely essential to avert timeouts in addition to saving valuable time. Another risk is phantom payjoin stuff after the timeout is expired if receiver-side does not know it has.
Fee Savings
The following observations might be generally applicable for both original and this v2 payjoin version. Fee-savings with payjoin is a tricky topic. Of course, overall a payjoin transaction is always cheaper than 2 separate transactions, since they get to share the overhead.
Additionally, without the receiver contributing to fees, the chosen fee rate of the PSBT (at the beginning) drops, and can lead to slower confirmation. From another perspective, a sender paying with payjoin pays higher fees for similar confirmation target. This has been observed in a production wallet years back. Given that total transaction time can extend to days, the fee environment itself might change, and all this must be considered when designing the UX.
Of course, there is nothing stopping the receiver from contributing to fees, but this idea is likely entirely novel to the bitcoin ecosystem (perhaps payments ecosystem in general) and the user base. Additionally, nominally it involves the user paying fees and tolerating delays just to receive bitcoin. Without explicit incentives/features that encourage receivers to participate, payjoining might seem like an unncessary hassle.
Overall, it seems that payjoin makes UX significant tradeoffs for important privacy (and potential fee-saving) benefits. This means that the UX might have to do significant heavy-lifting, to ensure that users are not surprised, confused or frustrated when they try to transact on-chain in a privacy-friendly feature. Good, timely communication, new features for consolidation & txn-cutthrough and guided user flows seem crucial to ensure payjoin adoption and for help make on-chain privacy a reality for users.
---------------
Original document available here. Reach out at
yashrajdca@proton.me,y_a_s_h_r_a_j.70on Signal, or on reach out in Bitcoin Design discord.https://stacker.news/items/981388
-
 @ 181ff6f7:7dc4fad2
2025-05-17 02:10:47
@ 181ff6f7:7dc4fad2
2025-05-17 02:10:47A plataforma 89p chegou para transformar a experiência de jogos online, oferecendo aos jogadores um ambiente de alta qualidade, repleto de opções diversificadas e recursos inovadores. Com uma interface amigável, tecnologia de ponta e uma vasta gama de jogos, a 89p é a escolha perfeita para quem busca diversão e emoção a qualquer hora do dia. Neste artigo, exploraremos as características dessa plataforma, os jogos disponíveis e a experiência do jogador que faz dela uma excelente opção.
Introdução à Plataforma 89p A 89p é uma plataforma de jogos online projetada para oferecer uma experiência única aos jogadores. Com um design intuitivo, fácil de navegar e totalmente otimizado para diferentes dispositivos, os usuários podem acessar a plataforma a partir de desktops, laptops e dispositivos móveis. A plataforma é conhecida por sua estabilidade, velocidade e suporte ao cliente de qualidade, garantindo que todos os aspectos da experiência do usuário sejam tratados com excelência.
O objetivo da 89pé oferecer aos seus jogadores uma experiência segura, confiável e divertida, com uma ampla gama de jogos que atendem a todos os gostos e preferências. Se você é fã de jogos de habilidade, jogos de azar ou opções mais descontraídas, a plataforma tem algo para todos.
Variedade de Jogos na Plataforma 89p Uma das grandes vantagens da 89p é a diversidade de opções de jogos. A plataforma conta com um catálogo extenso, com títulos das mais variadas categorias. Desde jogos de cartas, como pôquer e blackjack, até jogos mais modernos, como slots e jogos de mesa, a 89p garante que seus jogadores tenham acesso ao que há de melhor no mundo dos jogos online.
Além disso, a plataforma oferece jogos com temas e estilos diferentes, permitindo que cada jogador encontre opções que se adaptem ao seu estilo. A 89p também está constantemente atualizando seu portfólio de jogos, trazendo novas opções e versões aprimoradas, para que a experiência de jogar nunca se torne monótona.
A plataforma se destaca também pela qualidade gráfica dos seus jogos, que são desenvolvidos com tecnologia de última geração. Isso garante não só uma jogabilidade envolvente, mas também visuais impressionantes que tornam a experiência ainda mais imersiva. A jogabilidade é fluida, e os gráficos são de alta qualidade, com animações e efeitos especiais que aumentam ainda mais a diversão.
A Experiência do Jogador na 89p Na 89p, a experiência do jogador está no centro de tudo. A plataforma foi desenvolvida para ser fácil de usar, mesmo para aqueles que não têm muita experiência em jogos online. A navegação é simples, e a disposição dos jogos é organizada de maneira prática, permitindo que os jogadores encontrem rapidamente suas opções preferidas.
Outro ponto importante é o suporte ao cliente. A 89p oferece atendimento rápido e eficiente, com uma equipe de profissionais treinados para resolver quaisquer dúvidas ou problemas que possam surgir. O suporte está disponível 24 horas por dia, 7 dias por semana, garantindo que os jogadores tenham sempre a ajuda que precisam quando necessário.
Além disso, a plataforma se preocupa com a segurança de seus usuários. A 89p utiliza criptografia de última geração para proteger os dados dos jogadores, garantindo que suas informações pessoais e financeiras estejam sempre seguras. Isso é essencial para criar um ambiente confiável e tranquilo para os jogadores se concentrarem apenas na diversão.
Conclusão A 89p é uma plataforma de jogos online que oferece uma experiência completa, com uma grande variedade de jogos, suporte de alta qualidade e uma interface intuitiva. Se você está procurando uma nova forma de se divertir jogando online, a 89p é uma excelente escolha, proporcionando segurança, inovação e, claro, muita diversão.
-
 @ 57d1a264:69f1fee1
2025-05-16 05:38:28
@ 57d1a264:69f1fee1
2025-05-16 05:38:28LegoGPT generates a LEGO structure from a user-provided text prompt in an end-to-end manner. Notably, our generated LEGO structure is physically stable and buildable.
Lego is something most of us knows. This is a opportuity to ask where is our creativity going? From the art of crafting figures to building blocks following our need and desires to have a machine thinking and building following step-by-step instructions to achieve an isolated goal.
Is the creative act then in the question itself, not anymore in the crafting? Are we just delegating the solution of problems, the thinking of how to respond to questions, to machines? Would it be different if delegated to other people?
Source: https://avalovelace1.github.io/LegoGPT/
https://stacker.news/items/981336
-
 @ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03
@ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ 3bf0c63f:aefa459d
2024-01-14 14:52:16
@ 3bf0c63f:aefa459d
2024-01-14 14:52:16Drivechain
Understanding Drivechain requires a shift from the paradigm most bitcoiners are used to. It is not about "trustlessness" or "mathematical certainty", but game theory and incentives. (Well, Bitcoin in general is also that, but people prefer to ignore it and focus on some illusion of trustlessness provided by mathematics.)
Here we will describe the basic mechanism (simple) and incentives (complex) of "hashrate escrow" and how it enables a 2-way peg between the mainchain (Bitcoin) and various sidechains.
The full concept of "Drivechain" also involves blind merged mining (i.e., the sidechains mine themselves by publishing their block hashes to the mainchain without the miners having to run the sidechain software), but this is much easier to understand and can be accomplished either by the BIP-301 mechanism or by the Spacechains mechanism.
How does hashrate escrow work from the point of view of Bitcoin?
A new address type is created. Anything that goes in that is locked and can only be spent if all miners agree on the Withdrawal Transaction (
WT^) that will spend it for 6 months. There is one of these special addresses for each sidechain.To gather miners' agreement
bitcoindkeeps track of the "score" of all transactions that could possibly spend from that address. On every block mined, for each sidechain, the miner can use a portion of their coinbase to either increase the score of oneWT^by 1 while decreasing the score of all others by 1; or they can decrease the score of allWT^s by 1; or they can do nothing.Once a transaction has gotten a score high enough, it is published and funds are effectively transferred from the sidechain to the withdrawing users.
If a timeout of 6 months passes and the score doesn't meet the threshold, that
WT^is discarded.What does the above procedure mean?
It means that people can transfer coins from the mainchain to a sidechain by depositing to the special address. Then they can withdraw from the sidechain by making a special withdraw transaction in the sidechain.
The special transaction somehow freezes funds in the sidechain while a transaction that aggregates all withdrawals into a single mainchain
WT^, which is then submitted to the mainchain miners so they can start voting on it and finally after some months it is published.Now the crucial part: the validity of the
WT^is not verified by the Bitcoin mainchain rules, i.e., if Bob has requested a withdraw from the sidechain to his mainchain address, but someone publishes a wrongWT^that instead takes Bob's funds and sends them to Alice's main address there is no way the mainchain will know that. What determines the "validity" of theWT^is the miner vote score and only that. It is the job of miners to vote correctly -- and for that they may want to run the sidechain node in SPV mode so they can attest for the existence of a reference to theWT^transaction in the sidechain blockchain (which then ensures it is ok) or do these checks by some other means.What? 6 months to get my money back?
Yes. But no, in practice anyone who wants their money back will be able to use an atomic swap, submarine swap or other similar service to transfer funds from the sidechain to the mainchain and vice-versa. The long delayed withdraw costs would be incurred by few liquidity providers that would gain some small profit from it.
Why bother with this at all?
Drivechains solve many different problems:
It enables experimentation and new use cases for Bitcoin
Issued assets, fully private transactions, stateful blockchain contracts, turing-completeness, decentralized games, some "DeFi" aspects, prediction markets, futarchy, decentralized and yet meaningful human-readable names, big blocks with a ton of normal transactions on them, a chain optimized only for Lighting-style networks to be built on top of it.
These are some ideas that may have merit to them, but were never actually tried because they couldn't be tried with real Bitcoin or inferfacing with real bitcoins. They were either relegated to the shitcoin territory or to custodial solutions like Liquid or RSK that may have failed to gain network effect because of that.
It solves conflicts and infighting
Some people want fully private transactions in a UTXO model, others want "accounts" they can tie to their name and build reputation on top; some people want simple multisig solutions, others want complex code that reads a ton of variables; some people want to put all the transactions on a global chain in batches every 10 minutes, others want off-chain instant transactions backed by funds previously locked in channels; some want to spend, others want to just hold; some want to use blockchain technology to solve all the problems in the world, others just want to solve money.
With Drivechain-based sidechains all these groups can be happy simultaneously and don't fight. Meanwhile they will all be using the same money and contributing to each other's ecosystem even unwillingly, it's also easy and free for them to change their group affiliation later, which reduces cognitive dissonance.
It solves "scaling"
Multiple chains like the ones described above would certainly do a lot to accomodate many more transactions that the current Bitcoin chain can. One could have special Lightning Network chains, but even just big block chains or big-block-mimblewimble chains or whatnot could probably do a good job. Or even something less cool like 200 independent chains just like Bitcoin is today, no extra features (and you can call it "sharding"), just that would already multiply the current total capacity by 200.
Use your imagination.
It solves the blockchain security budget issue
The calculation is simple: you imagine what security budget is reasonable for each block in a world without block subsidy and divide that for the amount of bytes you can fit in a single block: that is the price to be paid in satoshis per byte. In reasonable estimative, the price necessary for every Bitcoin transaction goes to very large amounts, such that not only any day-to-day transaction has insanely prohibitive costs, but also Lightning channel opens and closes are impracticable.
So without a solution like Drivechain you'll be left with only one alternative: pushing Bitcoin usage to trusted services like Liquid and RSK or custodial Lightning wallets. With Drivechain, though, there could be thousands of transactions happening in sidechains and being all aggregated into a sidechain block that would then pay a very large fee to be published (via blind merged mining) to the mainchain. Bitcoin security guaranteed.
It keeps Bitcoin decentralized
Once we have sidechains to accomodate the normal transactions, the mainchain functionality can be reduced to be only a "hub" for the sidechains' comings and goings, and then the maximum block size for the mainchain can be reduced to, say, 100kb, which would make running a full node very very easy.
Can miners steal?
Yes. If a group of coordinated miners are able to secure the majority of the hashpower and keep their coordination for 6 months, they can publish a
WT^that takes the money from the sidechains and pays to themselves.Will miners steal?
No, because the incentives are such that they won't.
Although it may look at first that stealing is an obvious strategy for miners as it is free money, there are many costs involved:
- The cost of ceasing blind-merged mining returns -- as stealing will kill a sidechain, all the fees from it that miners would be expected to earn for the next years are gone;
- The cost of Bitcoin price going down: If a steal is successful that will mean Drivechains are not safe, therefore Bitcoin is less useful, and miner credibility will also be hurt, which are likely to cause the Bitcoin price to go down, which in turn may kill the miners' businesses and savings;
- The cost of coordination -- assuming miners are just normal businesses, they just want to do their work and get paid, but stealing from a Drivechain will require coordination with other miners to conduct an immoral act in a way that has many pitfalls and is likely to be broken over the months;
- The cost of miners leaving your mining pool: when we talked about "miners" above we were actually talking about mining pools operators, so they must also consider the risk of miners migrating from their mining pool to others as they begin the process of stealing;
- The cost of community goodwill -- when participating in a steal operation, a miner will suffer a ton of backlash from the community. Even if the attempt fails at the end, the fact that it was attempted will contribute to growing concerns over exaggerated miners power over the Bitcoin ecosystem, which may end up causing the community to agree on a hard-fork to change the mining algorithm in the future, or to do something to increase participation of more entities in the mining process (such as development or cheapment of new ASICs), which have a chance of decreasing the profits of current miners.
Another point to take in consideration is that one may be inclined to think a newly-created sidechain or a sidechain with relatively low usage may be more easily stolen from, since the blind merged mining returns from it (point 1 above) are going to be small -- but the fact is also that a sidechain with small usage will also have less money to be stolen from, and since the other costs besides 1 are less elastic at the end it will not be worth stealing from these too.
All of the above consideration are valid only if miners are stealing from good sidechains. If there is a sidechain that is doing things wrong, scamming people, not being used at all, or is full of bugs, for example, that will be perceived as a bad sidechain, and then miners can and will safely steal from it and kill it, which will be perceived as a good thing by everybody.
What do we do if miners steal?
Paul Sztorc has suggested in the past that a user-activated soft-fork could prevent miners from stealing, i.e., most Bitcoin users and nodes issue a rule similar to this one to invalidate the inclusion of a faulty
WT^and thus cause any miner that includes it in a block to be relegated to their own Bitcoin fork that other nodes won't accept.This suggestion has made people think Drivechain is a sidechain solution backed by user-actived soft-forks for safety, which is very far from the truth. Drivechains must not and will not rely on this kind of soft-fork, although they are possible, as the coordination costs are too high and no one should ever expect these things to happen.
If even with all the incentives against them (see above) miners do still steal from a good sidechain that will mean the failure of the Drivechain experiment. It will very likely also mean the failure of the Bitcoin experiment too, as it will be proven that miners can coordinate to act maliciously over a prolonged period of time regardless of economic and social incentives, meaning they are probably in it just for attacking Bitcoin, backed by nation-states or something else, and therefore no Bitcoin transaction in the mainchain is to be expected to be safe ever again.
Why use this and not a full-blown trustless and open sidechain technology?
Because it is impossible.
If you ever heard someone saying "just use a sidechain", "do this in a sidechain" or anything like that, be aware that these people are either talking about "federated" sidechains (i.e., funds are kept in custody by a group of entities) or they are talking about Drivechain, or they are disillusioned and think it is possible to do sidechains in any other manner.
No, I mean a trustless 2-way peg with correctness of the withdrawals verified by the Bitcoin protocol!
That is not possible unless Bitcoin verifies all transactions that happen in all the sidechains, which would be akin to drastically increasing the blocksize and expanding the Bitcoin rules in tons of ways, i.e., a terrible idea that no one wants.
What about the Blockstream sidechains whitepaper?
Yes, that was a way to do it. The Drivechain hashrate escrow is a conceptually simpler way to achieve the same thing with improved incentives, less junk in the chain, more safety.
Isn't the hashrate escrow a very complex soft-fork?
Yes, but it is much simpler than SegWit. And, unlike SegWit, it doesn't force anything on users, i.e., it isn't a mandatory blocksize increase.
Why should we expect miners to care enough to participate in the voting mechanism?
Because it's in their own self-interest to do it, and it costs very little. Today over half of the miners mine RSK. It's not blind merged mining, it's a very convoluted process that requires them to run a RSK full node. For the Drivechain sidechains, an SPV node would be enough, or maybe just getting data from a block explorer API, so much much simpler.
What if I still don't like Drivechain even after reading this?
That is the entire point! You don't have to like it or use it as long as you're fine with other people using it. The hashrate escrow special addresses will not impact you at all, validation cost is minimal, and you get the benefit of people who want to use Drivechain migrating to their own sidechains and freeing up space for you in the mainchain. See also the point above about infighting.
See also
-
 @ 181ff6f7:7dc4fad2
2025-05-17 02:10:09
@ 181ff6f7:7dc4fad2
2025-05-17 02:10:09A 7075Bet é uma plataforma de entretenimento digital inovadora, projetada para proporcionar aos jogadores uma experiência inesquecível com uma ampla variedade de jogos emocionantes. Com uma interface intuitiva e recursos que visam a comodidade do usuário, a 7075Bet se destaca no cenário de plataformas de entretenimento online, oferecendo uma experiência completa e envolvente. Neste artigo, exploraremos as funcionalidades dessa plataforma, os jogos que ela oferece e como ela se dedica a proporcionar a melhor experiência aos seus jogadores.
Plataforma de Entretenimento Inovadora
A 7075Bet foi criada com o objetivo de revolucionar a forma como os jogadores interagem com as plataformas de entretenimento online. Sua interface moderna e intuitiva permite que até mesmo iniciantes naveguem facilmente por todas as funcionalidades da plataforma. A plataforma oferece uma experiência fluída, com design responsivo que se adapta bem tanto em dispositivos móveis quanto em desktops.
O processo de registro é simples e rápido, permitindo que novos jogadores comecem a explorar a plataforma sem complicações. Além disso, a 7075betoferece diversas opções de pagamento, tornando o processo de depósitos e retiradas acessível e seguro para os usuários. Com um suporte ao cliente eficiente, os jogadores podem contar com a ajuda da equipe da plataforma sempre que necessário, garantindo uma experiência tranquila e sem contratempos.
Jogos Diversificados para Todos os Gostos
Na 7075Bet, os jogadores encontram uma vasta gama de opções de jogos, atendendo a todos os tipos de gostos e preferências. Se você é fã de jogos de mesa, a plataforma oferece várias opções clássicas, como blackjack e roleta, que podem ser jogadas de forma fácil e divertida. Esses jogos são projetados para proporcionar aos jogadores uma experiência envolvente, com gráficos e animações de alta qualidade que imitam a sensação de estar em um ambiente físico.
Para os fãs de jogos mais dinâmicos e rápidos, a 7075Bet também disponibiliza uma seleção de jogos eletrônicos e de vídeo. Desde caça-níqueis modernos até jogos com jackpots progressivos, cada título é projetado para manter os jogadores entretidos por horas. Os jogos apresentam temas inovadores, com designs criativos e recursos interativos que tornam a jogabilidade ainda mais divertida e recompensadora.
Além disso, a plataforma está sempre atualizando sua seleção de jogos, garantindo que os jogadores tenham acesso às novidades mais recentes do mercado. Isso demonstra o compromisso da 7075Bet em oferecer uma experiência de entretenimento atualizada e diversificada.
A Experiência do Jogador: Conforto e Segurança
A experiência do jogador é a prioridade na 7075Bet. A plataforma não só oferece uma grande variedade de jogos, mas também proporciona um ambiente seguro e confortável para seus usuários. Com medidas rigorosas de segurança, como criptografia de dados e autenticação de transações, os jogadores podem se sentir tranquilos ao fazer depósitos e retirar seus ganhos.
A experiência do jogador vai além dos jogos em si. A plataforma oferece promoções regulares, bônus de boas-vindas e programas de fidelidade que tornam a jornada ainda mais emocionante. A 7075Bet também oferece uma série de funcionalidades para que os jogadores possam personalizar suas preferências, ajustando notificações, definindo limites de jogo e participando de torneios exclusivos. Tudo isso contribui para que cada jogador se sinta único e tenha uma experiência personalizada.
Conclusão
A 7075Bet se destaca como uma plataforma de entretenimento online que oferece uma experiência completa e envolvente. Com uma interface amigável, uma seleção diversificada de jogos e um compromisso com a segurança e a satisfação dos jogadores, ela se tornou uma opção popular para aqueles que buscam diversão e emoção no mundo digital. Se você está em busca de uma plataforma de entretenimento que oferece algo para todos os gostos, a 7075Bet é, sem dúvida, uma escolha excelente.
-
 @ 57d1a264:69f1fee1
2025-05-14 09:48:43
@ 57d1a264:69f1fee1
2025-05-14 09:48:43Just another Ecash nutsnote design is a ew template for brrr.gandlaf.com cashu tocken printing machine and honoring Ecash ideator David Lee Chaum. Despite the turn the initial project took, we would not have Ecash today without his pioneering approach in cryptography and privacy-preserving technologies.
A simple KISS (Keep It Super Simple) Ecash nutsnote delivered as SVG, nothing fancy, designed in PenPot, an open source design tool, for slides, presentations, mockups and interactive prototypes.
Here Just another Nutsnote's current state, together with some snapshots along the process. Your feedback is more than welcome.
https://design.penpot.app/#/view?file-id=749aaa04-8836-81c6-8006-0b29916ec156&page-id=749aaa04-8836-81c6-8006-0b29916ec157§ion=interactions&index=0&share-id=addba4d5-28a4-8022-8006-2ecc4316ebb2
originally posted at https://stacker.news/items/979728
-
 @ 57d1a264:69f1fee1
2025-05-14 06:48:45
@ 57d1a264:69f1fee1
2025-05-14 06:48:45Has the architect Greg Chasen considered it when rebuilding the house just one year before the catastrophe? Apparently not! Another of his projects was featured on the Value of Architecture as properties with design integrity.
This is a super interesting subject. The historic character, livability, and modern disaster-resistance is a triangle where you often have to pick just one or two, which leads to some tough decisions that have major impacts on families and communities. Like one of the things he mentions is that the architect completely eliminated plants from the property. That's great for fire resistance, but not so great for other things if the entire town decides to go the same route (which he does bring up later in the video). I don't think there's any objectively right answer, but definitely lots of good (and important) discussion points to be had.
https://www.youtube.com/watch?v=cbl_1qfsFXk
originally posted at https://stacker.news/items/979653
-
 @ 3bf0c63f:aefa459d
2024-01-14 14:52:16
@ 3bf0c63f:aefa459d
2024-01-14 14:52:16bitcoinddecentralizationIt is better to have multiple curator teams, with different vetting processes and release schedules for
bitcoindthan a single one."More eyes on code", "Contribute to Core", "Everybody should audit the code".
All these points repeated again and again fell to Earth on the day it was discovered that Bitcoin Core developers merged a variable name change from "blacklist" to "blocklist" without even discussing or acknowledging the fact that that innocent pull request opened by a sybil account was a social attack.
After a big lot of people manifested their dissatisfaction with that event on Twitter and on GitHub, most Core developers simply ignored everybody's concerns or even personally attacked people who were complaining.
The event has shown that:
1) Bitcoin Core ultimately rests on the hands of a couple maintainers and they decide what goes on the GitHub repository[^pr-merged-very-quickly] and the binary releases that will be downloaded by thousands; 2) Bitcoin Core is susceptible to social attacks; 2) "More eyes on code" don't matter, as these extra eyes can be ignored and dismissed.
Solution:
bitcoinddecentralizationIf usage was spread across 10 different
bitcoindflavors, the network would be much more resistant to social attacks to a single team.This has nothing to do with the question on if it is better to have multiple different Bitcoin node implementations or not, because here we're basically talking about the same software.
Multiple teams, each with their own release process, their own logo, some subtle changes, or perhaps no changes at all, just a different name for their
bitcoindflavor, and that's it.Every day or week or month or year, each flavor merges all changes from Bitcoin Core on their own fork. If there's anything suspicious or too leftist (or perhaps too rightist, in case there's a leftist
bitcoindflavor), maybe they will spot it and not merge.This way we keep the best of both worlds: all software development, bugfixes, improvements goes on Bitcoin Core, other flavors just copy. If there's some non-consensus change whose efficacy is debatable, one of the flavors will merge on their fork and test, and later others -- including Core -- can copy that too. Plus, we get resistant to attacks: in case there is an attack on Bitcoin Core, only 10% of the network would be compromised. the other flavors would be safe.
Run Bitcoin Knots
The first example of a
bitcoindsoftware that follows Bitcoin Core closely, adds some small changes, but has an independent vetting and release process is Bitcoin Knots, maintained by the incorruptible Luke DashJr.Next time you decide to run
bitcoind, run Bitcoin Knots instead and contribute tobitcoinddecentralization!
See also:
[^pr-merged-very-quickly]: See PR 20624, for example, a very complicated change that could be introducing bugs or be a deliberate attack, merged in 3 days without time for discussion.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Token-Curated Registries
So you want to build a TCR?
TCRs (Token Curated Registries) are a construct for maintaining registries on Ethereum. Imagine you have lots of scissor brands and you want a list with only the good scissors. You want to make sure only the good scissors make into that list and not the bad scissors. For that, people will tell you, you can just create a TCR of the best scissors!
It works like this: some people have the token, let's call it Scissor Token. Some other person, let's say it's a scissor manufacturer, wants to put his scissor on the list, this guy must acquire some Scissor Tokens and "stake" it. Holders of the Scissor Tokens are allowed to vote on "yes" or "no". If "no", the manufactures loses his tokens to the holders, if "yes" then its tokens are kept in deposit, but his scissor brand gets accepted into the registry.
Such a simple process, they say, have strong incentives for being the best possible way of curating a registry of scissors: consumers have the incentive to consult the list because of its high quality; manufacturers have the incentive to buy tokens and apply to join the list because the list is so well-curated and consumers always consult it; token holders want the registry to accept good and reject bad scissors because that good decisions will make the list good for consumers and thus their tokens more valuable, bad decisions will do the contrary. It doesn't make sense, to reject everybody just to grab their tokens, because that would create an incentive against people trying to enter the list.
Amazing! How come such a simple system of voting has such enourmous features? Now we can have lists of everything so well-curated, and for that we just need Ethereum tokens!
Now let's imagine a different proposal, of my own creation: SPCR, Single-person curated registries.
Single-person Curated Registries are equal to TCR, except they don't use Ethereum tokens, it's just a list in a text file kept by a single person. People can apply to join, and they will have to give the single person some amount of money, the single person can reject or accept the proposal and so on.
Now let's look at the incentives of SPCR: people will want to consult the registry because it is so well curated; vendors will want to enter the registry because people are consulting it; the single person will want to accept the good and reject the bad applicants because these good decisions are what will make the list valuable.
Amazing! How such a single proposal has such enourmous features! SPCR are going to take over the internet!
What TCR enthusiasts get wrong?
TCR people think they can just list a set of incentives for something to work and assume that something will work. Mix that with Ethereum hype and they think theyve found something unique and revolutionary, while in fact they're just making a poor implementation of "democracy" systems that fail almost everywhere.
The life is not about listing a set of "incentives" and then considering the problems solved. Almost everybody on the Earth has the incentive for being rich: being rich has a lot of advantages over being poor, however not all people get rich! Why are the incentives failing?
Curating lists is a hard problem, it involves a lot of knowledge about the problem that just holding a token won't give you, it involves personal preferences, politics, it involves knowing where is the real limit between "good" and "bad". The Single Person list may have a good result if the single person doing the curation is knowledgeable and honest (yes, you can game the system to accept your uncle's scissors and not their competitor that is much better, for example, without losing the entire list reputation), same thing for TCRs, but it can also fail miserably, and it can appear to be good but be in fact not so good. In all cases, the list entries will reflect the preferences of people choosing and other things that aren't taken into the incentives equation of TCR enthusiasts.
We don't need lists
The most important point to be made, although unrelated to the incentive story, is that we don't need lists. Imagine you're looking for a scissor. You don't want someone to tell if scissor A or B are "good" or "bad", or if A is "better" than B. You want to know if, for your specific situation, or for a class of situations, A will serve well, and do that considering A's price and if A is being sold near you and all that.
Scissors are the worst example ever to make this point, but I hope you get it. If you don't, try imagining the same example with schools, doctors, plumbers, food, whatever.
Recommendation systems are badly needed in our world, and TCRs don't solve these at all.
-
 @ 57d1a264:69f1fee1
2025-05-14 06:12:19
@ 57d1a264:69f1fee1
2025-05-14 06:12:19We asked members of the design community to choose an artifact that embodies craft—something that speaks to their understanding of what it means to make with intention. Here’s what they shared.
A vintage puzzle box, a perfectly tuned guitar, an AI-powered poetry camera. A daiquiri mixed with precision. A spreadsheet that still haunts muscle memory. Each artifact tells a story: not just about the thing itself, but about the choices of the creator behind it. What to refine, what to leave raw. When to push forward, when to let go. Whether built to last for generations or designed to delight in a fleeting moment, the common thread is that great craft doesn’t happen by accident. It’s made.
On the application of craft
Even the most experienced makers can benefit from building structure and intention into their practice. From sharpening your storytelling to designing quality products, these pieces offer practical ways to uplevel your craft.
Read more at https://www.figma.com/blog/craft-artifacts/
originally posted at https://stacker.news/items/979644
-
 @ 181ff6f7:7dc4fad2
2025-05-17 02:09:35
@ 181ff6f7:7dc4fad2
2025-05-17 02:09:35Se você está em busca de uma plataforma confiável e emocionante para se divertir, a 777ua é uma excelente opção. Com uma interface amigável, uma vasta seleção de jogos e uma experiência personalizada para cada jogador, essa plataforma tem conquistado o coração de muitos entusiastas do entretenimento digital. Neste artigo, vamos explorar a introdução da plataforma, os jogos que ela oferece e a experiência do jogador, para ajudá-lo a entender por que a 777ua está se tornando cada vez mais popular.
A 777ua é uma plataforma de entretenimento online que oferece uma experiência de usuário moderna e dinâmica. Com um design intuitivo e recursos inovadores, a plataforma foi criada para atender tanto a iniciantes quanto a jogadores experientes. O seu foco está em proporcionar uma navegação fácil, rápida e divertida, sem complicações, permitindo que os usuários se concentrem no que realmente importa: a diversão.
Ao acessar a 777ua, o jogador é recebido com uma interface bem estruturada, que facilita a exploração dos diversos jogos disponíveis. A plataforma também é otimizada para dispositivos móveis, o que significa que você pode acessar seus jogos favoritos de qualquer lugar, a qualquer momento.
Além disso, a 777ua é comprometida com a segurança dos seus usuários. Com tecnologias de criptografia de última geração, seus dados pessoais e financeiros estão sempre protegidos, oferecendo uma experiência sem preocupações para todos os jogadores.
Jogos na 777ua: Variedade para Todos os Gostos Uma das maiores atrações da 777ua é a sua extensa gama de jogos. A plataforma oferece uma variedade impressionante de opções, incluindo jogos de mesa, slots, jogos de habilidade e muito mais. A qualidade gráfica e a jogabilidade dos títulos são excepcionais, proporcionando uma experiência imersiva e emocionante.
Entre os jogos mais populares da plataforma estão os jogos de cartas, como blackjack e pôquer, onde os jogadores podem testar suas habilidades contra outros usuários ou contra a própria plataforma. Para aqueles que preferem algo mais dinâmico, as máquinas de caça-níqueis são uma ótima escolha. Com temas variados e recursos especiais, esses jogos são conhecidos pela sua jogabilidade viciante e pelas grandes oportunidades de ganho.
Além disso, a 777ua também investe em títulos de jogos de habilidade, onde a estratégia e o raciocínio lógico fazem toda a diferença. Seja você um novato ou um veterano, sempre há algo para todos na 777ua.
Os jogos são atualizados regularmente, garantindo que os usuários tenham acesso às últimas novidades do mundo do entretenimento digital. Isso significa que você nunca ficará entediado, sempre haverá algo novo para experimentar.
A Experiência do Jogador: Diversão e Comodidade Na 777ua, a experiência do jogador é a prioridade. Desde o momento em que você entra na plataforma, é claro que a 777ua se preocupa em proporcionar uma experiência de alta qualidade. A navegação simples e a organização intuitiva permitem que você encontre facilmente o que procura. Você pode jogar seus jogos favoritos com poucos cliques e aproveitar um ambiente virtual imersivo e de alta performance.
Além disso, a 777ua oferece diversas opções de pagamento, para que os jogadores possam fazer depósitos e retiradas de maneira fácil e segura. A plataforma também oferece um suporte ao cliente excepcional, com uma equipe pronta para ajudar com qualquer dúvida ou problema que possa surgir.
Outro aspecto importante da experiência do jogador na 777ua é a comunidade de jogadores. Ao interagir com outros usuários, você pode trocar dicas, estratégias e até participar de competições e eventos exclusivos. A plataforma também oferece sistemas de recompensas e promoções para valorizar ainda mais a experiência do jogador, garantindo que cada visita à 777ua seja cheia de novidades e benefícios.
Conclusão: Por Que Escolher a 777ua? A 777ua se destaca como uma plataforma de entretenimento online completa, oferecendo uma enorme variedade de jogos, segurança, e uma experiência de usuário excepcional. Seja você um novato ou um jogador experiente, a plataforma é projetada para garantir diversão, emoção e oportunidades de ganho.
Com sua interface amigável, jogos de alta qualidade e uma experiência de jogador sem igual, a 777ua está rapidamente se tornando uma das plataformas mais populares e confiáveis. Não importa o tipo de jogo que você procura, a 777ua tem algo para você. Então, não perca tempo, entre agora e comece a explorar o mundo da 777ua!
-
 @ 9f9fda7f:e5e82a43
2025-05-17 10:32:54
@ 9f9fda7f:e5e82a43
2025-05-17 10:32:54Apache Kafka Architecture
Apache Kafka Architecture
Apache Kafka is a powerful distributed stream processing platform originally developed by LinkedIn, written in Scala and Java. In this article, I walk through the foundational concepts, design and architecture, concluding with hands-on coding examples using Node.js and the KafkaJS library.
Introduction to Kafka
Kafka enables the processing of real-time data streams in a distributed and scalable manner. It’s widely used in systems requiring reliable communication between components, especially for event-driven architectures and microservices.
However, these words sounds very markety and I like to deconstruct things to its basic first principles so that is what I’m going to do. This guide outlines the essential components, explains the core concepts like brokers, producers, consumers, and topics, and dives into more complex abstractions like partitions, consumer groups, and Kafka’s distributed nature.
Kafka Core Components
Here we discuss the fundamental components of Kafka.
Topics and Messages
Messages in Kafka are organized into logical categories called topics. Each topic is append-only and immutable (ie you cannot go back and edit a message). New data is added sequentially at the end. Disks love that.
There are two topics, one called users with two messages (John and Ed) and a Jobs with two messages Req1 and Req2.
Kafka Broker (Server)
The central server that receives and stores messages sent by producers and allow consumers to read the messages. Clients communicate with brokers via TCP, typically on port 9092.
Kafka broker hosts the topics and messages.
Producers and Consumers:
Producers connects to a broker, sends messages to the Kafka broker by specifying the topic.
Publisher pushes messages to the broker for a topic, messages go to the end.
Consumers connects to a broker, polls messages from a topic for a given broker for processing.
Customer polls messages based on a position
Partitions
I always say the best way to work with billions of rows is to avoid working with billions of row. Kafka is no different.
The topics in Kafka can be divided into partitions to allow data distribution and scalability. Each partition acts as a log that consumers read sequentially. Messages within partitions are identified by their offset, which is the message’s position in the log.
Partitioning
Partitioning enables parallel processing, you can have two consumers each processing a partition in parallel. While this allows scaling and improve reading throughput, it introduces complexity as producers and consumers must be aware of partitioning logic. A topic may have multiple partitions based on partition keys (e.g., A–M in partition 0, N–Z in partition 1).
Pub/Sub vs Queue Model
Kafka supports both pub/sub and queue-based messaging patterns:
- Queue: The topic can be treated as a queue, ie any message published to the queue will be consumed only once and popped from the queue. No two consumers can get the same message.
- Pub/Sub: The topic can be in publish-subscribe entity, ie any message published to the topic can be consumed by different consumers.
Kafka achieves this dual functionality using consumer groups. Each consumer in a group is assigned specific partitions, ensuring messages are processed only once per group.
To simulate a queue , all consumers are placed in the same consumer group (they all have the same group name). Whereas to simulate pub/sub mode you would place all consumers in unique group names.
Consumer Groups and Rebalancing
Each partition in a topic is assigned one consumer in a group. When multiple consumers join the same group, Kafka rebalances partitions among them. Each partition is consumed by only one consumer in a group. This allows horizontal scaling while ensuring order within each partition is maintained. Will demonstrate that in the code section.
Distributed Kafka Clusters and Zookeeper
Kafka operates as a distributed system with multiple brokers. Each broker can be a leader or follower for different partitions. The leader handles reads and writes, while followers replicate data.
Kafka originally relied on Zookeeper to manage broker coordination, metadata, and leader election. Zookeeper tracks which broker is the leader of which partition. However, Zookeeper introduces complexity and is being phased out in newer Kafka versions. Kafka 4.0 no longer has Zookeeper.
On Long Polling
You may ask, how does the consumer get the data the moment it is published to the topic/partition? I encourage you to first think of how could this be implemented.
One approach is push, ie the broker pushes the message to the consumer TCP connection. This approach is real-time, but overwhelms the consumer, as it needs to process the message.
Another approach is polling, ie the consumer every X milliseconds asks the broker, is there anything for me and the broker replies, yes here you go, or no nothing, this approach does allow the consumer to read at its own pace but may introduce severe network chatter, which lead to network bandwidth, it also may causes consumer to miss the real-time message, since the message may have came in to the broker between polls.
The final approach which Kafka went with is long polling which I talked extensively on my backend course. The consumer connects to the broker and sends a normal poll, if there is a message the broker replies back, if there isn’t the broker doesn’t respond with “no”, but instead just wait little bit more (configurable), this increases the chances that messages may arrive during this wait. Once we get a message the broker writes the response. Meanwhile the consumer feels like its poll request just took little longer.
Kafka, Docker and Node Example
We will use docker to install Kafka broker and Zookeeper single mode cluster. Then create a topic called “Users” with two partitions, produce some messages on both partitions and have consumers read from the partitions.
My docker host IP is 192.168.7.179, replace it with your own docker host IP.
You will need to have docker and Node installed to proceed
First we clone the repo and change IP address to your docker host.
```javascript
clone the repo
git clone https://github.com/hnasr/javascript_playground.git
change to the kafka directory
cd javascript_playground/kafka
edit docker-compose.yml, producer.js, topics.js and consumer.js change the 192.168.7.179 with your docker host ip.
cat starthere.txt ```
Spin up Zookeeper and Kafka containers using Docker commands.
```javascript services: zookeeper: image: zookeeper hostname: zookeeper ports: - 2181:2181 volumes: - zookeeper_data:/data - zookeeper_datalog:/datalog
kafka: image: ches/kafka restart: always hostname: localhost ports: - "9092:9092" environment: KAFKA_ADVERTISED_HOST_NAME: 192.168.7.179 ZOOKEEPER_IP: 192.168.7.179 KAFKA_OFFSETS_TOPIC_REPLICATION_FACTOR: 1 ALLOW_PLAINTEXT_LISTENER: 1 depends_on: - zookeeper volumes: - kafka_data:/kafka
volumes: zookeeper_data: zookeeper_datalog: kafka_data: ```
javascript docker-compose upCreate a topic called
MyUserswith two partitions, we will use kafkajs module to connect to the kafka broker.```javascript //const Kafka = require("kafkajs").Kafka const {Kafka} = require("kafkajs")
run(); async function run(){ try { const kafka = new Kafka({ "clientId": "myapp", "brokers" :["192.168.7.179:9092"] })
const admin = kafka.admin(); console.log("Connecting.....") await admin.connect() console.log("Connected!") //A-M, N-Z await admin.createTopics({ "topics": [{ "topic" : "MyUsers", "numPartitions": 2 }] }) console.log("Created Successfully!") await admin.disconnect(); } catch(ex) { console.error(`Something bad happened ${ex}`) } finally{ process.exit(0); }} ```
javascript node topics.jsProduce some messages with a producer, the messages are user names. I have the messages starting with letters
```javascript //const Kafka = require("kafkajs").Kafka const {Kafka} = require("kafkajs") const msg = process.argv[2]; run(); async function run(){ try { const kafka = new Kafka({ "clientId": "myapp", "brokers" :["192.168.7.179:9092"] })
const producer = kafka.producer(); console.log("Connecting.....") await producer.connect() console.log("Connected!") //A-M 0 , N-Z 1 const partition = msg[0] < "N" ? 0 : 1; const result = await producer.send({ "topic": "Users", "messages": [ { "value": msg, "partition": partition } ] }) console.log(`Send Successfully! ${JSON.stringify(result)}`) await producer.disconnect(); } catch(ex) { console.error(`Something bad happened ${ex}`) } finally{ process.exit(0); }} ```
javascript node producer.js Adam node producer.js Zackjavascript HusseinMac:kafka HusseinNasser$ node producer.js Adam Connecting..... Connected! Send Successfully! [{"topicName":"MyUsers","partition":0,"errorCode":0,"offset":"0","timestamp":"-1"}] HusseinMac:kafka HusseinNasser$ node producer.js Zack Connecting..... Connected! Send Successfully! [{"topicName":"MyUsers","partition":1,"errorCode":0,"offset":"0","timestamp":"-1"}]Implement a consumer that subscribes to the topic and handles messages with long polling.
Note that I hard coded a consumer group name “test” in the consumer.js file. Running the consumer.js file will create a new consumer on the MyUsers topic and it will be responsible for both partitions. You can note this from the response"memberAssignment”:{“MyUsers”:[0,1]}
javascript HusseinMac:kafka HusseinNasser$ node consumer.js Connecting..... Connected! {"level":"INFO","timestamp":"2025-04-13T14:29:36.102Z","logger":"kafkajs","message":"[Consumer] Starting","groupId":"test"} {"level":"INFO","timestamp":"2025-04-13T14:29:58.411Z","logger":"kafkajs","message":"[Runner] Consumer has joined the group","groupId":"test","memberId":"myapp-901679c6-034c-4efd-bc4d-cb5fc5bc9e6e","leaderId":"myapp-901679c6-034c-4efd-bc4d-cb5fc5bc9e6e","isLeader":true,"memberAssignment":{"MyUsers":[0,1]},"groupProtocol":"RoundRobinAssigner","duration":22307} RVD Msg Adam on partition 0 RVD Msg Zack on partition 1Now assume we run another consumer, which will also have the same group. Kafka will rebalance the group and assign a partition for each consumer so they parallel process.
Note the memberAssignment property for each consumer.
```javascript HusseinMac:kafka HusseinNasser$ node consumer.js (consumer 1) {"level":"ERROR","timestamp":"2025-04-13T14:31:09.360Z","logger":"kafkajs","message":"[Connection] Response Heartbeat(key: 12, version: 0)","broker":"192.168.7.179:9092","clientId":"myapp","error":"The group is rebalancing, so a rejoin is needed","correlationId":39,"size":6} {"level":"ERROR","timestamp":"2025-04-13T14:31:09.361Z","logger":"kafkajs","message":"[Runner] The group is rebalancing, re-joining","groupId":"test","memberId":"myapp-901679c6-034c-4efd-bc4d-cb5fc5bc9e6e","error":"The group is rebalancing, so a rejoin is needed","retryCount":0,"retryTime":308} {"level":"INFO","timestamp":"2025-04-13T14:31:09.382Z","logger":"kafkajs","message":"[Runner] Consumer has joined the group","groupId":"test","memberId":"myapp-901679c6-034c-4efd-bc4d-cb5fc5bc9e6e","leaderId":"myapp-901679c6-034c-4efd-bc4d-cb5fc5bc9e6e","isLeader":true,"memberAssignment":{"MyUsers":[1]},"groupProtocol":"RoundRobinAssigner","duration":21}
HusseinMac:kafka HusseinNasser$ node consumer.js (consumer 2) Connecting..... Connected! {"level":"INFO","timestamp":"2025-04-13T14:31:07.599Z","logger":"kafkajs","message":"[Consumer] Starting","groupId":"test"} {"level":"INFO","timestamp":"2025-04-13T14:31:09.383Z","logger":"kafkajs","message":"[Runner] Consumer has joined the group","groupId":"test","memberId":"myapp-6c861d03-879d-4b7b-81a1-1e2cd1c15c83","leaderId":"myapp-901679c6-034c-4efd-bc4d-cb5fc5bc9e6e","isLeader":false,"memberAssignment":{"MyUsers":[0]},"groupProtocol":"RoundRobinAssigner","duration":1783} ```
Let us publish one message for each partition and see what happens.
javascript node producer.js Adamy node producer.js Zackery```javascript (consumer 1) RVD Msg Zackery on partition 1 (consumer 2) RVD Msg Adamy on partition 0
```
What happens if more consumers than partitions are available? As per testing, new consumers won’t get any partitions assigned. But a consumer group rebalance may reassign partitions.
Kafka Pros and Cons
By understanding the architecture and design of Apache Kafka we know the fact it is performs well for writes (producing messages), because of the append-only nature. And having the consumer aware of the position to where to read from makes reads also fast. Kafka scales well with partitioning and handle fault tolerant with the distributed nature.
However, no software is free of limitations, with all these features added to Kafka, complexity is unavoidable. Producers needs to be aware of the partitions which introduces complexity in producing messages. The need for distributed architecture, replication introduces depedancies on an external component (Zookeeper) which adds more complexity and even latency. All of this makes Kafka difficult to install, maintain and manage.
Note that Kafka 4.0 that was release in March 2025 has completely removed Zookeeper in favor of a raft based replication between brokers.
Conclusion
Now that you know the basics of Apache Kafka, you will understand its power and its limitations. That is the most important thing. Anything on top of Kafka uses these fundamentals.
If you enjoyed this article, check out my backend and database courses.
https://stas.layer3.press/articles/c11f511b-29f5-4612-a308-004c44183c7b
-
 @ 6fc114c7:8f4b1405
2025-05-17 00:54:52
@ 6fc114c7:8f4b1405
2025-05-17 00:54:52Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28idea: "numbeo" with satoshis
This site has a crowdsourced database of cost-of-living in many countries and cities: https://www.numbeo.com/cost-of-living/ and it sells the data people write there freely. It's wrong!
Could be an fruitful idea to pay satoshis for people to provide data.
-
 @ c9badfea:610f861a
2025-05-16 23:58:34
@ c9badfea:610f861a
2025-05-16 23:58:34- Install Breezy Weather (it's free and open source)
- Launch the app, tap Add A New Location and search for your city
- Review the providers for each weather source
- Optionally, add more locations by tapping the + icon
- Enjoy the weather updates
ℹ️ To receive notifications for weather alerts, tap ⚙️, then Notifications and enable Notifications Of Severe Weather Alerts
-
 @ d360efec:14907b5f
2025-05-12 04:01:23
@ d360efec:14907b5f
2025-05-12 04:01:23 -
 @ 57d1a264:69f1fee1
2025-05-14 05:56:15
@ 57d1a264:69f1fee1
2025-05-14 05:56:15Shanghai: Bus Stops Here
A new crowd-sourced transit platform allows riders to propose, vote on, and activate new bus lines in as little as three days.
From early-morning school drop-offs to seniors booking rides to the hospital, from suburban commuters seeking a faster link to the metro to families visiting ancestral graves, Shanghai is rolling out a new kind of public bus — one that’s designed by commuters, and launched only when enough riders request it.
Branded “DZ” for dingzhi, or “customized,” the system invites residents to submit proposed routes through a city-run platform. Others with similar travel needs can opt in or vote, and if demand meets the threshold — typically 15 to 20 passengers per trip — the route goes live.
More than 220 DZ routes have already launched across all 16 city districts. Through an online platform opened May 8, users enter start and end points, preferred times, and trip frequency. If approved, routes can begin running in as little as three days.
Continue reading at https://www.sixthtone.com/news/1017072
originally posted at https://stacker.news/items/979637
-
 @ 04c3c1a5:a94cf83d
2025-05-13 16:49:23
@ 04c3c1a5:a94cf83d
2025-05-13 16:49:23Testing Testing Testing
This is just a test this is just a test this is just a test This is just a test this is just a test this is just a test This is just a test this is just a test this is just a test This is just a test this is just a test this is just a test This is just a test this is just a test this is just a test This is just a test this is just a test this is just a test This is just a test this is just a test this is just a test

nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqg7waehxw309anx2etywvhxummnw3ezucnpdejz7ur0wp6kcctjqqspywh6ulgc0w3k6mwum97m7jkvtxh0lcjr77p9jtlc7f0d27wlxpslwvhau
| | | | | ------------------------ | - | - | | Quick'hthbdoiwenweuifier | | | | 1. Little | | |
ghtgehg
gwefjieqhf
MUCH BETTER
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Lightning and its fake HTLCs
Lightning is terrible but can be very good with two tweaks.
How Lightning would work without HTLCs
In a world in which HTLCs didn't exist, Lightning channels would consist only of balances. Each commitment transaction would have two outputs: one for peer
A, the other for peerB, according to the current state of the channel.When a payment was being attempted to go through the channel, peers would just trust each other to update the state when necessary. For example:
- Channel
AB's balances areA[10:10]B(in sats); Asends a 3sat payment throughBtoC;AasksBto route the payment. ChannelABdoesn't change at all;Bsends the payment toC,Caccepts it;- Channel
BCchanges fromB[20:5]CtoB[17:8]C; BnotifiesAthe payment was successful,Aacknowledges that;- Channel
ABchanges fromA[10:10]BtoA[7:13]B.
This in the case of a success, everything is fine, no glitches, no dishonesty.
But notice that
Acould have refused to acknowledge that the payment went through, either because of a bug, or because it went offline forever, or because it is malicious. Then the channelABwould stay asA[10:10]BandBwould have lost 3 satoshis.How Lightning would work with HTLCs
HTLCs are introduced to remedy that situation. Now instead of commitment transactions having always only two outputs, one to each peer, now they can have HTLC outputs too. These HTLC outputs could go to either side dependending on the circumstance.
Specifically, the peer that is sending the payment can redeem the HTLC after a number of blocks have passed. The peer that is receiving the payment can redeem the HTLC if they are able to provide the preimage to the hash specified in the HTLC.
Now the flow is something like this:
- Channel
AB's balances areA[10:10]B; Asends a 3sat payment throughBtoC:AasksBto route the payment. Their channel changes toA[7:3:10]B(the middle number is the HTLC).Boffers a payment toC. Their channel changes fromB[20:5]CtoB[17:3:5]C.CtellsBthe preimage for that HTLC. Their channel changes fromB[17:3:5]CtoB[17:8]C.BtellsAthe preimage for that HTLC. Their channel changes fromA[7:3:10]BtoA[7:13]B.
Now if
Awants to trickBand stop respondingBdoesn't lose money, becauseBknows the preimage,Bjust needs to publish the commitment transactionA[7:3:10]B, which gives him 10sat and then redeem the HTLC using the preimage he got fromC, which gives him 3 sats more.Bis fine now.In the same way, if
Bstops responding for any reason,Awon't lose the money it put in that HTLC, it can publish the commitment transaction, get 7 back, then redeem the HTLC after the certain number of blocks have passed and get the other 3 sats back.How Lightning doesn't really work
The example above about how the HTLCs work is very elegant but has a fatal flaw on it: transaction fees. Each new HTLC added increases the size of the commitment transaction and it requires yet another transaction to be redeemed. If we consider fees of 10000 satoshis that means any HTLC below that is as if it didn't existed because we can't ever redeem it anyway. In fact the Lightning protocol explicitly dictates that if HTLC output amounts are below the fee necessary to redeem them they shouldn't be created.
What happens in these cases then? Nothing, the amounts that should be in HTLCs are moved to the commitment transaction miner fee instead.
So considering a transaction fee of 10000sat for these HTLCs if one is sending Lightning payments below 10000sat that means they operate according to the unsafe protocol described in the first section above.
It is actually worse, because consider what happens in the case a channel in the middle of a route has a glitch or one of the peers is unresponsive. The other node, thinking they are operating in the trustless protocol, will proceed to publish the commitment transaction, i.e. close the channel, so they can redeem the HTLC -- only then they find out they are actually in the unsafe protocol realm and there is no HTLC to be redeemed at all and they lose not only the money, but also the channel (which costed a lot of money to open and close, in overall transaction fees).
One of the biggest features of the trustless protocol are the payment proofs. Every payment is identified by a hash and whenever the payee releases the preimage relative to that hash that means the payment was complete. The incentives are in place so all nodes in the path pass the preimage back until it reaches the payer, which can then use it as the proof he has sent the payment and the payee has received it. This feature is also lost in the unsafe protocol: if a glitch happens or someone goes offline on the preimage's way back then there is no way the preimage will reach the payer because no HTLCs are published and redeemed on the chain. The payee may have received the money but the payer will not know -- but the payee will lose the money sent anyway.
The end of HTLCs
So considering the points above you may be sad because in some cases Lightning doesn't use these magic HTLCs that give meaning to it all. But the fact is that no matter what anyone thinks, HTLCs are destined to be used less and less as time passes.
The fact that over time Bitcoin transaction fees tend to rise, and also the fact that multipart payment (MPP) are increasedly being used on Lightning for good, we can expect that soon no HTLC will ever be big enough to be actually worth redeeming and we will be at a point in which not a single HTLC is real and they're all fake.
Another thing to note is that the current unsafe protocol kicks out whenever the HTLC amount is below the Bitcoin transaction fee would be to redeem it, but this is not a reasonable algorithm. It is not reasonable to lose a channel and then pay 10000sat in fees to redeem a 10001sat HTLC. At which point does it become reasonable to do it? Probably in an amount many times above that, so it would be reasonable to even increase the threshold above which real HTLCs are made -- thus making their existence more and more rare.
These are good things, because we don't actually need HTLCs to make a functional Lightning Network.
We must embrace the unsafe protocol and make it better
So the unsafe protocol is not necessarily very bad, but the way it is being done now is, because it suffers from two big problems:
- Channels are lost all the time for no reason;
- No guarantees of the proof-of-payment ever reaching the payer exist.
The first problem we fix by just stopping the current practice of closing channels when there are no real HTLCs in them.
That, however, creates a new problem -- or actually it exarcebates the second: now that we're not closing channels, what do we do with the expired payments in them? These payments should have either been canceled or fulfilled before some block x, now we're in block x+1, our peer has returned from its offline period and one of us will have to lose the money from that payment.
That's fine because it's only 3sat and it's better to just lose 3sat than to lose both the 3sat and the channel anyway, so either one would be happy to eat the loss. Maybe we'll even split it 50/50! No, that doesn't work, because it creates an attack vector with peers becoming unresponsive on purpose on one side of the route and actually failing/fulfilling the payment on the other side and making a profit with that.
So we actually need to know who is to blame on these payments, even if we are not going to act on that imediatelly: we need some kind of arbiter that both peers can trust, such that if one peer is trying to send the preimage or the cancellation to the other and the other is unresponsive, when the unresponsive peer comes back, the arbiter can tell them they are to blame, so they can willfully eat the loss and the channel can continue. Both peers are happy this way.
If the unresponsive peer doesn't accept what the arbiter says then the peer that was operating correctly can assume the unresponsive peer is malicious and close the channel, and then blacklist it and never again open a channel with a peer they know is malicious.
Again, the differences between this scheme and the current Lightning Network are that:
a. In the current Lightning we always close channels, in this scheme we only close channels in case someone is malicious or in other worst case scenarios (the arbiter is unresponsive, for example). b. In the current Lightning we close the channels without having any clue on who is to blame for that, then we just proceed to reopen a channel with that same peer even in the case they were actively trying to harm us before.
What is missing? An arbiter.
The Bitcoin blockchain is the ideal arbiter, it works in the best possible way if we follow the trustless protocol, but as we've seen we can't use the Bitcoin blockchain because it is expensive.
Therefore we need a new arbiter. That is the hard part, but not unsolvable. Notice that we don't need an absolutely perfect arbiter, anything is better than nothing, really, even an unreliable arbiter that is offline half of the day is better than what we have today, or an arbiter that lies, an arbiter that charges some satoshis for each resolution, anything.
Here are some suggestions:
- random nodes from the network selected by an algorithm that both peers agree to, so they can't cheat by selecting themselves. The only thing these nodes have to do is to store data from one peer, try to retransmit it to the other peer and record the results for some time.
- a set of nodes preselected by the two peers when the channel is being opened -- same as above, but with more handpicked-trust involved.
- some third-party cloud storage or notification provider with guarantees of having open data in it and some public log-keeping, like Twitter, GitHub or a Nostr relay;
- peers that get paid to do the job, selected by the fact that they own some token (I know this is stepping too close to the shitcoin territory, but could be an idea) issued in a Spacechain;
- a Spacechain itself, serving only as the storage for a bunch of
OP_RETURNs that are published and tracked by these Lightning peers whenever there is an issue (this looks wrong, but could work).
Key points
- Lightning with HTLC-based routing was a cool idea, but it wasn't ever really feasible.
- HTLCs are going to be abandoned and that's the natural course of things.
- It is actually good that HTLCs are being abandoned, but
- We must change the protocol to account for the existence of fake HTLCs and thus make the bulk of the Lightning Network usage viable again.
See also
- Channel
-
 @ 266815e0:6cd408a5
2025-05-16 20:52:42
@ 266815e0:6cd408a5
2025-05-16 20:52:42Streams are the key to nostr
Loading events from a nostr relay is probably the most inconsistent way of loading data I've had to work with, and that's only loading from a single relay. the problem gets exponentially more complicated once you try to load events from multiple relays
Unlike HTTP nostr does not have a simple flow with timeouts built in. events are sent back one at a time and can fail at any point or have massive (10s) gaps between them
The key is to use streams. something that starts, emits any number of results, then maybe errors or completes. luckily it just so happens that JavaScript / TypeScript has a great observable stream library called RxJS
What is an observable
An
Observablein RxJS is stream a of data that are initialized lazily, which means the stream is inactive and not running until something subscribes to it```ts let stream = new Observable((observer) => { observer.next(1) observer.next(2) observer.next(3) observer.complete() })
// The stream method isn't run until its subscribed to stream.subscribe(v => console.log(v)) ```
This is super powerful and perfect for nostr because it means we don't need to manage the life-cycle of the stream. it will run when something subscribes to it and stop when unsubscribed.
Its helpful to think of this as "pulling" data. once we have created an observable we can request the data from it at any point in the future.
Pulling data from relays
We can use the lazy nature of observables to only start fetching events from a nostr relay when we need them
For example we can create an observable that will load kind 1 events from the damus relay and stream them back as they are returned from the relay
```typescript let req = new Observable((observer) => { // Create a new websocket connection when the observable is start let ws = new WebSocket('wss://relay.damus.io')
ws.onopen = () => { // Start a REQ ws.send(JSON.stringify(['REQ', 'test', {kinds: [1], limit: 20}])) }
ws.onmessage = (event) => { let message = JSON.parse(event.data) // Get the event from the message and pass it along to the subscribers if(message[0] === 'EVENT') observer.next(message[1]) }
// Cleanup subscription return () => { ws.send(JSON.stringify(['CLOSE', 'test'])) ws.close() } }) ```
But creating the observable wont do anything. we need to subscribe to it to get any events.
ts let sub = req.subscribe(event => { console.log('we got an event' event) })Cool now we are pulling events from a relay. once we are done we can stop listening to it by unsubscribing from it
ts sub.unsubscribe()This will call the cleanup method on the observable, which in turn closes the connection to the relay.
Hopefully you can see how this work, we don't have any
open,connect, ordisconnectmethods. we simply subscribe to a stream of events and it handles all the messy logic of connecting to a relayComposing and chaining observables
I've shown you how we can create a simple stream of events from a relay, but what if we want to pull from two relays?
Easy, lets make the previous example into a function that takes a relay URL
```ts function getNoteFromRelay(relay: string){ return new Observable((observer) => { let ws = new WebSocket(relay)
// ...rest of the observable...}) } ```
Then we can "merge" two of these observables into a single observable using the
mergemethod from RxJSThe
mergemethod will create a single observable that subscribes to both upstream observables and sends all the events back. Think of it as pulling events from both relays at once```ts import { merge } from 'rxjs'
const notes = merge( getNoteFromRelay('wss://relay.damus.io'), getNoteFromRelay('wss://nos.lol') )
// Subscribe to the observable to start getting data from it const sub = notes.subscribe(event => { console.log(event) })
// later unsubscribe setTimeout(() => { sub.unsubscribe() }, 10_000) ```
But now we have a problem, because we are pulling events from two relays we are getting duplicate events. to solve this we can use the
.pipemethod and thedistinctoperator from RxJS to modify our single observable to only return one version of each eventThe
.pipemethod will create a chain of observables that will each subscribe to the previous one and modify the returned values in some wayThe
distinctoperator takes a method that returns a unique identifier and filters out any duplicate values```ts import { merge, distinct } from 'rxjs'
const notes = merge( getNoteFromRelay('wss://relay.damus.io'), getNoteFromRelay('wss://nos.lol') ).pipe( // filter out events we have seen before based on the event id distinct(event => event.id) ) ```
Now we have an observable that when subscribed to will connect to two relays and return a stream of events without duplicates...
As you can see things can start getting complicated fast. but its also very powerful because we aren't managing any life-cycle code, we just subscribe and unsubscribe from an observable
Taking it to an extreme
Hopefully at this point you can see how powerful this is, we can think of almost any data loading pattern as a series of observables that pull data from upstream observables and stream it back to the original subscriber.
Here is a quick sketch of what it could look like to load user profiles. each node is an observable that "pulls" data from its child node ending with the "connect websocket" or "load from database" nodes which do the work of making a relay connection
Conclusion
All this might seem pretty simple and straight forward, but its been a long six month of learning for me. I've had to completely rethink how data and nostr events should be handled in a client and how to avoid screwing up and shooting myself in the foot with these powerful tools.
If you want to give RxJS a try I would encourage you to checkout the nostr sdk I've been building called applesauce
Its uses RxJS for pretty much everything and has the simplest and most flexible relay connection API I've seen so far (mainly no life-cycle management)
-
 @ c9badfea:610f861a
2025-05-16 20:15:31
@ c9badfea:610f861a
2025-05-16 20:15:31- Install Obtainium (it's free and open source)
- Launch the app and allow notifications
- Open your browser, navigate to the GitHub page of the app you want to install, and copy the URL (e.g.
https://github.com/revanced/revanced-managerfor ReVanced) - Launch Obtainium, navigate to Add App, paste the URL into App Source URL, and tap Add
- Wait for the loading process to finish
- You can now tap Install to install the application
- Enable Allow From This Source and return to Obtainium
- Proceed with the installation by tapping Install
ℹ️ Besides GitHub, Obtainium can install from additional sources
ℹ️ You can also explore Complex Obtainium Apps for more options
-
 @ d360efec:14907b5f
2025-05-10 03:57:17
@ d360efec:14907b5f
2025-05-10 03:57:17Disclaimer: * การวิเคราะห์นี้เป็นเพียงแนวทาง ไม่ใช่คำแนะนำในการซื้อขาย * การลงทุนมีความเสี่ยง ผู้ลงทุนควรตัดสินใจด้วยตนเอง
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ 5391098c:74403a0e
2025-05-13 16:47:48
@ 5391098c:74403a0e
2025-05-13 16:47:48(Textículo em prosa erudita sobre a Ideologia Anarco-Capitalista-Cristã)
https://davipinheiro.com/01-escravos-da-cara-inchada/
A cultura #Woke apropriou-se da imagem sobre a #escravidão. Quando uma pessoa aculturada imagina um #escravo, vem em sua mente a imagem de um ser humano negro, magro e flagelado. Para quem enxerga além das cortinas da mentira, vem em sua mente a imagem de um ser humano de qualquer etnia, gordo e doente.
Democracia, péssimo regime de governo assim classificado pelo seu próprio idealizador: Platão em A República, é o grito da hienas de dentes arreganhados para ampliação do regime escravocrata fomentado pelos #GlobalistasSatanistas.
Um escravo da cara inchada é todo aquele ser humano ignorante inconsciente que alimenta esse sistema em troca de intoxicantes como flúor¹, cloro, glutamato monosódico, gordura trans, corantes, conservantes, refrigerantes, bebidas alcoólicas, psicotrópicos e remédios sintomáticos, tudo embrulhado com mentiras reiteradas.
Como consequência, após os 18 anos de idade o corpo do #EscravoDaCaraInchada sucumbe à tamanha intoxicação e passa a inchar, sendo fisicamente perceptível sua condição de escravo da cara inchada tanto à olho nú quando por reconhecimento facial de qualquer pseudo inteligência artificial.
O círculo vicioso da #EscravidaoDemocratica é tão simples e tosco como o “pão e circo romano”, Mesmo assim é muito difícil para o escravo da cara inchada perceber a própria condição tamanha é sua intoxicação física e mental.
Se um Anarco-Capitalista-Cristão (#Ancapcristão) chega para um escravo da cara inchada e explica sobre esses intoxicantes como instrumento de escravização, dificilmente o escravo da cara inchada irá acreditar pois diferentemente do antigo e aposentado chicote, o novo instrumento da escravidão não dói de imediato e os próprios efeitos da intoxicação impedem-no de raciocinar com clareza.
Portanto, para que os #GlobalistasSatanistas obtivessem sucesso na democratização da escravidão, tiveram que criar um chicote químico e uma ideologia favorável. Quanto às etapas utilizadas para formação dessa ideologia no inconsciente coletivo passo a elencar as 6 grandes mentiras em ordem cronológica:
(1ª etapa) Iluminismo: distanciamento de #Deus e seus ensinamentos, criação de sociedades secretas, exacerbação do ser humano perante o criador na tentativa de projetar o ser humano como seu próprio deus, tornando-o responsável sobre os rumos naturais do planeta. Assim formou-se a base ideológica para o materialismo, ambientalismo, feminismo, controle populacional e ideologia de gêneros;
(2ª etapa) Materialismo: perda do propósito espiritual e do sentido da vida², o que passa a importar são apenas as coisas materiais, acima inclusive do próprio ser humano. A perpetuação da espécie também fica em segundo plano. Assim formou-se a base ideológica para o ambientalismo, feminismo, controle populacional e ideologia de gêneros;
(3ª etapa) Ambientalismo: redução do ser humano à mero câncer do planeta superlotado, atribuído-lhe a responsabilidade por qualquer desastre natural. Assim formou-se a base ideológica para o controle populacional e ideologia de gêneros;
(4ª etapa) Feminismo: enfraquecimento do ser humano por meio da sua divisão em duas categorias: macho e fêmea, os quais são inimigos e não cooperadores. A ideia de igualdade de gêneros é tão antagônica que beira ao conflito cognitivo³: Eles querem separar para dizer que são iguais... Ora, como não pode haver diferenças entre os gêneros se eles são fisicamente e mentalmente diferentes? Nesse diapasão, mesmo não sendo os estados nacionais os arquitetos da escravidão democrática e sim meros fantoches dos globalistas satanistas, o voto feminino foi fundamental para aprovação de leis misândricas com o fito de acelerar a destruição da base familiar do escravo da cara inchada. Importante mencionar que a base familiar dos globalistas satanistas continua sendo patriarcal. Assim formou-se a base ideológica para o controle populacional e ideologia de gêneros;
(5ª etapa) Controle Populacional: “Crescei e multiplicai-vos” é o caralho, Deus não sabe de nada (Iluminismo), o que importa é o dinheiro e filho é caro (Materialismo), para que colocar mais um ser humano nesse planeta doente e superlotado (Ambientalismo), além disso o sexo oposto é meu inimigo (Feminismo). Essa é base ideológica que antecede a ideologia de Controle Populacional, ainda reforçada pela apologia à castração, já que em todas as mídias produzidas com patrocínio oculto de capital globalista satanista tentam normalizar a castração do homem (perda da capacidade de reprodução) desde em desenhos infantis até grandes produções cinematográficas, ora em tom de humor ora em tom de tortura. Assim os escravos da cara inchada do sexo masculino perderam sua identidade, essência e desejo de ser o que são, formando-se a base ideológica para o homossexualismo, ou seja, para a ideologia de gêneros.
(6ª etapa) Ideologia de Gêneros: É a cereja do bolo para os planos do Diabo (Anjo invejoso de Deus que quer destruir a maior criação: nós). Enquanto os globalistas satanistas, dentro de sua sábia ignorância, acreditam estarem chefiando a democratização da escravidão, na verdade também não passam de meros fantoches do Anjo Caído. Com a sexta e última etapa de mentiras para extinção da humanidade (#apocalipse) posta em prática através da Ideologia de Gêneros, fecha-se o ciclo vicioso de mentiras que se auto justificam: Se #Deus não presta, o que vale são os bens materiais, o ser humano é um câncer no planeta, o sexo oposto é inimigo e ter filhos é uma péssima ideia e ser homem másculo é crime, então ser #homossexual é a melhor opção, inclusive vamos castrar os meninos antes da puberdade sem o consentimento dos pais ou mães solo. Aqui também há uma grande bifurcação do círculo vicioso de mentiras, qual seja o gritante conflito cognitivo³: Se todos os homens deixarem de ser másculos, quem vai comer os #gays afeminados? Ou se todas as mulheres deixarem de ser femininas, quem as #sapatonas irão comer? E o pior, se todos passem a ser homossexuais quem vai perpetuar a espécie? Seremos extintos no lapso temporal de apenas uma geração, pois a fraudulenta medicina moderna jamais terá a capacidade de gerar bebês de chocadeira à tempo.
É interessante enxergar que mesmo os Globalistas Satanistas, dentro de sua sábia ignorância, acreditando estarem democratizando a escravidão em benefício próprio, na verdade apenas estão fomentando o apocalipse, ou seja sua própria extinção. Também não terão qualquer lugar especial no inferno, sinônimo de mal é mentira. Portanto os #GlobalistaSatanistas são meros fantoches do #Diabo enganador, tão submissos quanto o Escravo da Cara Inchada…
Interessante também enxergar que o livre arbítrio é uma condição obrigatória para independência da criação (anjo e ser humano). Todos somos livres para escolher entre o bem e o mal, se iremos ser escravos de #Deus ou escravos do Diabo. Se assim não fosse, inexistiria criação pois seríamos mera extensão da consciência do #Criador, em outras palavras: para que exista uma criação, essa deve ter a capacidade de decisão de forma independente, o chamado livre arbítrio.
Com base nisso, temos que não cabe à nos fazer qualquer revolução, tudo está normal, a luta entre o bem e o mal sempre irá existir pois um não existe sem o outro. Nos cabe apenas escolher o lado. Nesse contexto, tenho a seguinte mensagem destinada à você para encerrar o presente Textículo Anarco-Capitalista-Cristão:
------ > Se você for um ANARCO-CAPITALISTA-CRISTÃO passe esta palavra à diante para que a verdade atinja o maior número de ignorantes inconscientes possível;
------ > Se você for um GLOBALISTA SATANISTA, vai viver sua vida, desfrutar da própria fortuna e pare de ser fantoche o Diabo, mentiram para você: não terá qualquer lugar especial quando morrer;
------ > Se você for um ESCRAVO DA CARA INCHADA e não entendeu o que eu disse, por favor me pergunte ou debata comigo, terei o prazer em lhe ajudar a enxergar a verdade. Pare de trabalhar por dinheiro fiduciário, passe a aceitar #Monero e #Bitcoin em troca do seu trabalho, pois isso é o único jeito de sermos financeiramente livres, se tiver alguma dúvida sobre #criptomoedas me pergunte e terei o prazer e ensinar. Se ainda assim você se recusa a enxergar a verdade exposta aqui, por favor aceite #Monero e #Bitcoin quando for dar o seu cú. Ou melhor, cometa suicídio, já que você é um câncer no planeta, salve a natureza.
(Davi Pinheiro)
¹ - https://davipinheiro.com/teoria-da-conspiracao-o-fluor-na-agua-e-usado-para-controlar-mentes-revista-super-interessante-editora-abril/
² - https://davipinheiro.com/qual-o-sentido-da-vida/
³ - https://davipinheiro.com/entendendo-as-referencias-cruzadas-do-pensamento/
PREZADOS AMIGOS, DIVULGUEM ESTE ARTIGO. ABAIXO SEGUE A LISTA DOS 500 BRASILEIROS MAIS ATIVOS NO NOSTR NOS ÚLTIMOS MESES PARA TODOS SEGUIREM-SE ENTRE SI E FORTALECER NOSSA COMUNIDADE DE LÍNGUA BRASILEIRA (se você não estiver na lista interaja para ser adicionado):
npub1u2e0qzjsjw9suxcdkeqrydr07xzsyx8mzp469augc0a29aeasfdq8fx67q npub1xt25e4pakq6x4w44p9kw2vlfwv4zpc9hg7xsnrq53hl0za4ag2qs09cwcs npub17hgdpn9xnt5zyxlx8pz0uuus8d23pxwr9a5vq96nw5nawx20zxnsj6fym6 npub1arnth7tuxw060c74adaf08jam6kttn24wfdse9wyg2c7waycwezqszr2mz npub1qg8j6gdwpxlntlxlkew7eu283wzx7hmj32esch42hntdpqdgrslqv024kw npub10q0axre6n3ew64pen99x0qkrh70yxfx6w3grwvkhk4kz9dp8m3ssltvs6f npub1sf2se74xlzf7f7clm3dg28npaxghdy6pguzpsut30fjpwuaxrxcsrnhr57 npub19ychr8yknmje69r645sgd8j0epx2rdgdyl7feagcnmrwkaedzffqtrcznl npub1k86zp0778x7cjng50et5z76xdwxy0tgfn5amnrwrd6mda8uln4lq78ua23 npub13src792wxm8nrhqzu555uxuktfffzcqx78s3pc9zefcdjgwvm3pqsddz4j npub1uw04lzuqx42gk0xc4m8advfmuqlz8nv7dqpuyq4gcv8r304lwvnq2m5ew2 npub1fw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqvq2rfr npub1nkenffr9eslkzplds3lwcz7xeq67w6a9qcjlfsvspj7tnhuq3kgsram48g npub1w66drr2qta67gyt7la6fgglsdvk3xx3nndsz4k5wfcal8jq0ze7sqcxdpd npub12xq6exra99hg6tuefx3yysszqudaljvy6eyxqz8tpt7038gpaqus7lfuyy npub17tvf04z759dsyecdtmk70tevla7vua9e3sr88lgnl7put97764zq708q0m npub1rzajeq88urk58nh0n7gqknr2agrx34xu4en0k8hm43fl8h2khp6sk0v3y4 npub1yspe4ly5p9dlfv4vevm0evpag8ljkaay3x3clj8gtvxlsvpwrrrs6h47mx npub107a0nwr3lsj9kdy3jdq570jzcv95y0qzuuhrvcgrpsnq2h4xsclqzy7v4g npub14reqsqss7wp06k390a547pkqrlc0w6uzelm9gpwxze7p8z8x3awsuthvzz npub18fh6flnjt9aa3jlnp5k3kd9zr6v5mlpeczhdx4qheytfyyqfpe7s2y0lzm npub1lafcm7zm35l9q06mnaqk5ykt2530ylnwm5j8xaykflppfstv6vysxg4ryf npub1s00wyzkfrjcclawx225k7wrxd74369vxdcdhy88j89yhrxssfclqulxf93 npub1rmq4kl4dfvp4kt937f9mz60ywkwv467585vnesm3ctqz9krkksrqg4ran0 npub1d7r5su48a8m5k389fd6rwy9cvhlyycmg3pl2g60q5zmgvmr3xreq098mu2 npub1r8lsve0d5yezxq52fjj90kwz76xcweyxlx9uwhsrpd6gt7uk4edscl4fdr npub19ljjj23d7fgy0gujlnh26a293p6uwawrrnpg7jlqfnhnard322gssd2rnj npub1u484zct2rxyknscgnnxrwpuk3f2j679x8tdysvxh659whv99g35saq9xjt npub1gpd868cejawju35epkayavfkqfuykt3820xe678m2vqfqj8v7ges2t4umk npub172fwxt8nnauv2c6leevl0rq4mk87c5vu4mm4fqef58xt390jqxfs6ua7vz npub1gmdrkx4lgwzyqr6krqyykg9r2kpasftuu2x98ncvs9xz9cjhfgcsxns0xz npub1sfzc94dhlkrj6m9tdkle4glyazhtajjsj9qhjv279an06nr74uvqzka6js npub18rdvxdw773852gyl4kjkr5xmg44p9l0jywdk6cq8axl3k9yh59fsu3g8aj npub167h7xtt7tkfvr9mn9d09s4u6r4l0y7rr355jpjg55lg4mpdghsasa9c47v npub1q4qjda5zm33743dd4mewnx6j049hgry7ls4nvh54clcnax3wsnzqv7c5lw npub1mjckw2qsqemdnhz7ul63vpcd79fmar49r8y7fh0tffva767yx07qq68xkn npub1ry2uv7qwu840qx4fg38zzfrl6dfgaudn6d8s7trpf3sj8nx0vaaquj5qrj npub1zqw2ymcy9txda2wzuka7yx6vlyvuwe7k2pldxpxxx660nhf65tusxzdcp6 npub1fjr0qa7rdhll7cfpgdcsz5nry2gy92u7a8gr0ku390n69865ec0qxwcral npub1wc4rc9wxl2gfzxl384g0cw3f79nrms0sfdpe02y7aasy7c3we4sqd0qywr npub19x5l76266vfen827fudaampuuupkejg9vls88hld8nv4w4sq59lsqlal37 npub1gc24vefdu60d3e3yxg8mhu52hxxpcykesk85y8mez8llj23kpehszdmu3j npub1u9ja9ymqmaw7mn9tnmrsnpx0f9j6hs59kxd9de363jvadjamzd9qg3ek4k npub1lzt7pmhvg7hl23emv22g4d7cs9jyglkqpr7lf3n8rcz0evkacg2s6n4jjf npub1p22hyejtr60rdrmjvql5k8fyv8lkq8exzw5mkkx3qcwqcu6979aqvhpqlq npub15p6p9l5upa0y0aj5nwf7lnud2regh00az9u4a4fmgyh8ukyue8kq7xuzp7 npub187dlu8g04kk8adc309vwn3lxsj63fmaty5vmdyrsvzx2fcxg70pqfszj4z npub1adfs8z9rlk6dzwm44522ge0gf367t6s6x30nrulp0xq6wsglyxssxqwyva npub1wqh4j2lvkd0fz342he0jr2d8eqrjwlqsv42azw6utqnpkrjv72xqylx32z npub1n9e2cy50jk900hdzvxt4cjhn80qwzxuer93aylhfdc76gwksr2lsqt36ww npub1styn4qvw4h4s92pcntrffm5dhe889h3hanwjpv66r4ue7gd3xutqk9hpc6 npub157v53ahyyxh4mp38v363chz9lrrw8um9m0tyhqzjujz8m4pmr42s9sk9u8 npub1alq86fku99p0rgq6s0cwwe9lsa8vdvu4d6r7d6j6cyuysf2r76hsh9tt37 npub18cvuxxvd2a6gt76etnte5vtws7a5a4xeqgt03qcs0u46nfws0vzskrnwu9 npub1mlu4qvm8j7gqamukz98l832ghgktyj0whqrxfx89625m3p30haqq5racjk npub1l8tlpvn3kka3nm2qpk96amsuy2kr5kl9eusd54fpn3yjnefrnpaq2j5t9v npub1jtnuszgjayga0pzvm3t7z9pantcnyxzacu30mhvw4dk0lkkvhxrsgvfgw5 npub1z73hklrdpa0n5z663mvnu0afxhlegpt5exmkg9u0nmd32ktqs7fq3prv27 npub1tshn5e5h0ud3l6vegwrce2er2tuhxangx4yvx4q04uheznxxgp6qg9dx2n npub136aeqeuum2t8cjgfnpxwfkgf5e8fd95h39uqkenrr6u0yl3upg9skvkfq8 npub1pkjyqg0am9qyjwg772ue4hhshaf6gwgz4psnptlg9v8lk6st2naqct3ll5 npub1kvzyrn6zvvdh9jnvfzc6e86s0zpntvg0e9f0v340e59u2rut99zsuq9fl9 npub168dqt5c8ue3uj8ynlk0lhwalnp7uy39lvzf9tm09wy3htxwmw7qq5nerj4 npub1cajs9cz6r43rmn0y8v8cgeuuj2lfhftvxcq05f8efc22hr5fnwmshx0pvw npub1uu0qk8f7xv7egc6tf9kk3mkx99u2leldgzz0trl77uymvv8n8ahqtd6309 npub1t8a7uumfmam38kal4xaakzyjccht4y5jxfs4cmlj0p768pxtwu8skh56yu npub10wlfumja930vzz4jhh9vc6t3wy8ay7thg8mt9qcptlp5leqfmazqn79ee9 npub1tx8wamjvhaqme29rujkd4v978ck8d3ud7gxa9zzqtjftpfn9p5vs27a2lg npub1e5pneqe2je07e5sk00g8urqa66eljg74t4llv4htp6vq5f8kv2zsqrtway npub1nk7gygwkcfpf9hdjhkgyqszcgwyzmcrqhd9tr7zzczkm5ga79xusmm5qjt npub1p3pna34zku4fqe9mzyvhhffladjjxcug7jn20wm5rnccpjezn4ks0zaw4u npub1j4vyl5kadajpgxh2wrnfk2wvg25jhnv78s0mrs6ckuhft9uzqe7s9wpcgc npub1hfg3tsmmp7g3u5cw6mzg0n9andehmgel6jug486eppsr0rqx4a3qlp7yfm npub1zks89kfxmxv0s4sa7rj8yyd6ld8ncsqusm993678vq9ut73hn7uqhmecsf npub1hzt3p8ap8s4nnqjhha37z5q3jdc9lfg90js0crmg8u5lncnaqpzsdn75p5 npub12em9q547gfga2tkhuzc65ufrn5h9ndu270d7xnh0nkcz2gtvq4sqwutpy3 npub12fh76ppgs5g2srtvgewe9fprdsk2y6g42wf0sg2y0ucjxqq9l0dsy5n8wl npub1arjgv76ld978cya3k6xz24nuxkuezuqrsmy73x0gaxdlu7pxv4lq8npp2g npub1zpmtwh0esa4esnc4p6rn5vhx7wcfw8z0ky8nzczj6k46drsmm47s0zzlyh npub156zse25dzgt65kq472nfkfpwgqvf6vuw8ur0s0ny7zmzw4xqd68q3p4sem npub1pwyy6rwh9smlurdmfg7yy2lce43jlv9ac7l9zay723dyfx4m649ql85u04 npub13j4jtgrm0dtsfzecx4khzz5a8ykgdd374qewewj0ksfmenps67lqz2yr8a npub1dmdlkhqnzmde0ultsq72hnn8h6gjfrkfeud4hecjg8fg8pugzctsjwqas0 npub1yqq7mwccr6wv7vmhehgh4n9kwn55r9gneydhdu6249pntguacegsjgwevp npub1u79u7zxlz2flmwpdt59xsvv5syreavzdyu9llkg07swtf24a4ayq5g0uud npub1eezyd5p7n9vse3yv5k8vh068dutpjf7d9zuk6azegeh5ypvp270qqr8fam npub1s0p3y6rvmt5m6jf6zt96kl0c80x0fy396d8h3cvtsxpqq7lf7wwsgw780n npub1kcf4p6e8k0rkjtaaghu765647z58qu0wfpgxnqptlwg2pm30skzsm2mct0 npub10uqpae32d6t4xhcgmzkc5gkna3hf9xclpzf3q6kfusz5q8j5ruqs5tdemg npub1jldq9dk8kgtlr3akv8re00znkfyzq59t0yceuu6q0tdfxzmusarsfxfunp npub1ksp960nd2vhxxp4lw7unnhujy6mknd0mpw2sh7xuj4m963a2u03qw776l8 npub188qkhpvqhne68rwu878jta5a8uh3vl4mcmfp44nppydfz0td9tqqa5h3cm npub1e008u7wmf0gppsnzupclhzh4mexp90addmdu0wu9glyk0y6msvxskyd3yq npub1crtd3zn3ek0cwne036s0xfqgs6ywuutqdcwxl5k4csv57jsmlgfsjq9039 npub1u4r4hx3y820p8g00u65tpggk2rd5qkd0d3ukt2yvgwyhcd0qvymqweyx75 npub18e7t2damcrfe60empcnye5z896wf9fk478rgrdcawvv23hqtd8es3yg772 npub1s5uqfqur0jlnp9z32ag90e9p5y60z0e8ruryun6u8gy9c38s7caqqqjxvt npub1q9fawsk02d7ffc47l92peuasy9q23ganvs00aqfagxz9rgk5g3usy92n3g npub18qhe55gump3d8ff2xzugpeaxkq6gfc498hr6at2jlsert0h9qkvqquqmve npub1cj9w34dn6nyazvhtq9srms5rf9rj4tapmqlwc5d5k3cwk34vy8dqewkvj6 npub1wvkx5ckpcxmxvc9wd0q576qssle3ed40c4z5rpetwy8fqssq8k3qdhh3yl npub1wnpc03cvexrv7tqnz4amk5zpyxw30nat3xav8nna89j92h25q53sls0g5w npub1938qus3z7jxs4u5x6gpyf7pwavnvnvrhmlfv2jqryy43qf0mdgpqlrtyfq npub1gnvha9zemx47e3paehu59ssqjkkpkc0n6ugdufmkl9ahgd3qhajs6mfs4m npub1cha5p8ytujflljhet2k34sctnqyl3n5w74wnuy7c6dvyv870twas9xnugj npub1h4d7986rjexvgaqsv8zm4s88dekkacs9uadtad6zp8n38nkdszysj45nmc npub1wcuv2wqn3uypzx7f98vavt2gqz4f4qkzm28fgj4qpwgj3yfjghks0patgl npub14hq5lgadtyy9dhvtszq46dnl0s0xwdddqr7e32rdqqhma8a4xhsspxjjzu npub17rzgm20v9hf4m2hemlau5fzepyanwd5h3zxc0wkwq7y38s3g8uqs49lrut npub1l5sgjcjruwec2y2lxd23vj34qe2kkxyqnact76tsq5kzdtcmke0s4cz0uu npub1ylw08gevzgvwasypcs2lvmssfqyt46xzgul7lwvkssm76ehgq47qrn4xxk npub13t2th7tr0uxwc8mfkkr5dqmfrg5hmmdfnfjfhs4z2xal9z6hpe9q6xn9ph npub1239p46pv99lt94yfzu4xkh4u3vqr2k7rnmcc8zz64p6m8g0mva8qcxr0hj npub1r2eehghv6syvdhezrlln25fnz90clgdkcagqw87c9r735zlnhuaq8dpvwp npub1sd5wp8ufsttwk3c575gnakufgaeg3x4f4r5d84pun9n09yr7zq8s735ezh npub18txjwp7dj9hjwk972c32sj5xmngnutguvtg2r66a3g5rgw2s88xq3799uq npub1247x2zmsp8e766cy39gkuzywfq6ea89wd6sgvuh8lywrrvzvdqtsv9573z npub1mu2tx4ue4yt7n7pymcql3agslnx0zeyt34zmmfex2g07k6ymtksq7hansc npub152wtu2y9a5wlz74v88ahls2xq0g493gz5jx0wat9vfgxqzjfzl6qdazlty npub18yyc9l68tk6zsq63wmnzf3862l3xfckds38tq44egwl5l4g0nqeszhj50p npub15rdytrwdsc62qmvsc28xhzdxs5u35utlexg3tc3mtzm23ka4hzmsthe64f npub13je2r5t0s4uszds4lc5e87n77xngluwkjt0hesduvch0vk206gcsa0d03t npub10jjcalyj6a67qfxrax2mwpmsnrlles6qhk23j0dyc76h27gag05syya4qn npub155kdyaltpxaek29wkeza9prkr0t398ayn24wlp6pg68z57s8l67qka6ly8 npub1uk5ne4u0ey8s8tg8czceg70yw9jlzvk74y804wd3vaa3ncm5l9tsl2cjqc npub1q09ysz8xhfe0x0n2y77u6xem9whtsk5hgswz7s0lrj9znn8eksqqzzpsyy npub1rm8uwmhs7s9n3jqzzd92mwwgr8gca4p9x0u8vu8m5n5eppqj88fstspqh6 npub1e8antmtxy0vs2pjd6kah99lpy44ztads4m0udpf07vauvr7larzsf76w9j npub1e0ngk7s4nygt46cpmdrc63f3mfgjcp8edxh0f8vpp6zd5hwax4qq0mykcp npub1rksqdj6tpjx4ddcyc9v3jw458u9y83hk789jqy2j8h58jusv0mgscx389d npub1q2f2nlq5kxthrcsww2zmytyzal325gsvrv0aeg8fqj54z4kyrxgsylesz9 npub100t4hmfxs467q3cwqd5f3sej9zhm2edd3kcn57hj0kag3n49geusm5zt87 npub13et8ay8ny99mygd8ymznczusrhfrhhzzs8jdlep9q98r8uway9asl62v4r npub1qeydnlt70d29q3axc3h5v3spfntl74jukw9r6zy9s8ms6a82mupqgnr2y5 npub1n9hr9s73atxmjm0muz45ghwutvf2kc00lq2fa58rm9y80mpdqxmq73mdc0 npub145cgkka2733cmxn86khjshwyxz6ahgjp0ek9gp3fc2k7y3penkqq45ccpu npub1z24p8ghllrl4jxyw8juggm3cfrpn8vvfxxsjzjj4tuaz0qfkeqkstnk760 npub1h6mtmjw2au827vs99zlykn0tdhm3hpyffjgnaq8fsvjzem430hesd3zw5p npub13u9wq6td5qvj2dajmkjplz0ytvt4j7zvuyjg6kl9xqt5wznqghvqrptnlq npub1x7j0x34k2cguw8qk07hlgtpcdd22k0p4nfmuy3sk53mw7n5p4dws97mh3q npub1rlgz4nrqjvy7skd640reu9f9ckv5gzg4dmheeuq4u9dux42t7lys88svf3 npub1j5peadcc3as7ht6tszt47z2z3rec5py39y23cemrs47czyfxddnsskqnav npub1ymjhm0kxwldyx3f599d0cjvpcwdyfw7rmruyn8m2qnfhlu8mn4mspdwhqk npub1gaqn62wk22gesxfczv4q30kg3e2f6cqzdml645rwdyas6uaz3wdqexzlgl npub1z9vh6x3h5d99wvrjxw036ehg27cc37837f7dz4lr933euzu4pt3qn5874u npub1axy5sgkdz50hqrt266cl95qp7e5n9q6qmxguj0ry6mhpmu23t80s9nvqug npub1yvjmvxh2jx07m945mf2lu4j5kswr0d63n0w6cjddj3vpkw4unp4qjarngj npub1993fqzsar7lydy6lc8sztj5pxzeckttsf7m7dzjpcfvuu44uavksdks9p7 npub16s7exzaa4le983mjvnw7jfatum0jfxqtpfk2uqdel3c4q97uqznst6hyar npub15mptsgelg8rn5tjw5ltmdy8vmglws4fulr0kaghpv7t2jj8qzjks2mecva npub1yjvs58t4tgnmn98m4y2s64jferzv77p037zmwed8wzdful29a6esyajtwa npub1ctmkhtvw7rwk425sm4mqx6ak86aama7c6z8yxczfhgkwfv2fq7xq4mcr38 npub1f9jys8kppch9sceykam7p7uecpyam7ajm87wrgnndhjtj6jlp5vqe7y207 npub1k67tmzt34d6klra3ykrhkpvu0y8g8rlzv0egpgrry0xxcauxqzestwyz59 npub1x49ytzhkslwq6680jqsng7dy79vh8alsqpapr73m3akn0qerhj3ql7s2w3 npub1m2us7cgdufhg30yw6kawugwt5slp8kh9ed88dn7q5gtq5y20f95s9s25vt npub13sdds5pcp344k5mhfch7ltc4a8737uxqw9c47wfe08kkrnm3rhssm60637 npub1qfamw8qmsekxxu8pj5kfa960sgwsc86wys84gqxkzkzld8e6hk3qtvv7kq npub1tsxemx456uadxs4nsqenmquvws53290eg2gejrhvx7w965c779mslf7pds npub1ymxlmrd2yd59g7x4uejzsgmn4xlglu0schl39m2mjx5nzfzl2hcs73hn6g npub1qd05jn0jxlzplx33xjtzstvgeus9dk9405kwqf79vu00czwyvghqf08md5 npub1n5sl69j0w6c79tut2anqf69tkfevr065kzjt4n2rv2gres3q45ysmnj5nc npub10qjw7zw8m6yq4sr53watq4u8y47eef28jsyd0tmyhyfy4pjhntgqva7d9t npub1k6n2ghwu0afld0tnl2p43q7wtu2u9hln6e89ruv9a2y5deej06dskek6xy npub1ax4szvq26em2klfqj6hr38009x6k6m7nhe2z7mq0xs4xszetxe2s6964q4 npub1645w5cevetsz2364mss575panjuaa5ffh89ax4tp6u7x0tr2xlhsc29g25 npub1ys9j7sws8vccfwjctlqu7kx2hlfmkcxmjxmdttfl29edxv6xgelqkaffe4 npub1h4fnky04vkfkyac8shhmy0fwkrhuha65c5ec2ggvv03zv7pm64ls9x5vag npub1ueenpne5qhkvr4l9rw3c2ls2f6lgm7gh7f7ssl73l5yqt7um6uwsyatgml npub1krcpj4r4gp28vswfc4gztr5gku58c2eyhll47tyz5y2hhl6jyjwqduv9mr npub125nh0nkr0czuzkpjkqvjwc7mxuuvusr4n7a3kthjyfeer70eac0qpy5lsx npub1qcr5atkc2u04wx80pdyfnnwrttrw0taaz8hst3qt573j44yzxcvqkl339x npub1x96qzppsymujfyzn4dmkl08qgcr3aw7f2tt0xlmgyudfaggeq7zsh0yghv npub1l56z85xvaplh3033l8h2x9thypamu0d2hyqnxkw0ujuntqm8asaqh99sza npub1wh30wunfpkezx5s7edqu9g0s0raeetf5dgthzm0zw7sk8wqygmjqqfljgh npub1kqd90mglkp0ltmc5eacd0claqvnayaklkvzkdhx7x84w9uavplxszvrlwd npub1ly9cmpxs5kyrhnc946rlxmyj397pvcp3606zgvh3kvukmqveaxmqgwdwct npub1papvv8nyg68m73wae3u25lvxw5wfz2htpzk7j85z8yng3xqqvntqc5n9vf npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 npub16y2de3wvy2xgj3238r8h8g96hwtqsfm72sxcfw2t4c5xfjwnm4ms5y8uyd npub1ln4q6lzdwzxnvuv0a2gnfcxrfhwyfpcrp8tj5a403mwptq8r8clsq2znta npub1e0jya9z5wu68dzgxqeg7gal9ytgwvr63evtchv4a4wr8u5dcvs6s6vfwgm npub158dcjddhtq29ezyd3j5qyc70xyzyzujg02kcrla706fs52zcahaszql9ha npub1gayzxecnek73hm695d8tu94n2q3xnlucu9gwr2zqnql090rkautqq7ne7s npub1hvtyspm7n7nea59lhe2fdvwd0rqw7de20fl365wklsg4jsmrpwrqe6yaeh npub1hsr44v6satu5qkjcua36u8a8ng7fhh9ljv8mmnhvkf0a6407nhtq2k4ths npub18s8ym4ajt3rfwa0yn39m70k603j8a7wkhylhewzcjhtfheu8dnrqzwv677 npub1zdwjkqtwkst8y3mjj848hjh7tuqwqp7uvcfxzrl43gyx2k7pkz2s4p88cz npub1xq0pc34qq99yawjxl7rsqx7wgs4x3088tkwwle5kz3jqwf0ggyuqxx5et7 npub1dgx9jmq5sn4w96qnrgps7f5egjfpu5npnswazsaq98ryafkdjucshaaej8 npub1s6ms8dqxc4s2e6yawg20lkrpk9dxazz9qsaernpxndc2axua26rsva6lha npub19rxp2h2c96h9y79nhsu8p9yn4f79k8q76z40v8x6g0j8mcmex7jsu4whlq npub1fnvuz4rad0sc6ueflq33kj242hqe65da40zug7u5nryvjdeg0xqsl4y86t npub1e2d8f64kaxepfqncve7gy72vam3h66vmfwaqnalekv8zmh3qar4sz34p0k npub1krahyq9me8aglq54cfffylgnj0sy0q02emv9zr4csc94kz3qajxsmwu7lj npub1qn8rpsky3t8v5dn30rycfwpktwclm544nlef98tg23drgk022a4qtzekjd npub14p529xk3dmtyqp25slasulxx5p6yu2js6lz0072qu77c54cz6pesq2qsuv npub1mxlypddvhxdatdjdh2twejz7d8lkf90350f2zhzcunhmu7pgw9yq9033ss npub18lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vets0hcfsz npub160mrpl505fmse22eue6v23k4u4z0yyw37hpf3j73z97jtq50rapqx9q0ac npub1ve32zawsazgn9ukyr0trw4u5zk5z9ravgq9g06ml4gfzuvuzrvyq2mfzr3 npub1c0dysexhhd09e65rvmeecx0dpn6c7lq4yp99f3h4ktnr4vvrez5ql3h0y0 npub1758748kzgkp5vrt2u8vdgx462kt9f5p2x84xwljm4svadq9xc84sl9yk27 npub1rg7x6lh3zurejwnhxljdh8td2uhnhucx3jhle565eh7x94aqn03qrwrm9s npub14nefrmsdvn72qq5f3zqpdsh068ufk02e3t79ukga457p0v796chq7xrakx npub1l04nl239dn9wps24a753xq38h3wtlaa7vxmqatf9y0g6vzae6u0s27vwl8 npub1mezldzxnv6lszd7vlh60k0cqgxca7s08x5akyvln9fhz58jyfzsscyepuv npub1a76u90rr5tfdn9vf3sg574g0vftz4p5vu5r9t57c9atpwt64jkps0h4qya npub18g9zwmrdjcf6mkz7zpavmcx46r3h9ydxv2urwc9kqvha7vzght6swffxry npub12y8v5es4g8ynms5495l448977l25puf39wj9has66f7yg8xkhakqn89g0n npub1gustav0kvwh9zlz22ns7y6utwt3s2747mh5s6ja7v622tl09megq9heczp npub1t62k7smt3nad7s3rzhkrcvzlmheerk8p3qrpjwj32c9lzfmz5ksqaegpck npub1cuvc5stpvpeljeveqlk9u6tp3z3qams2w9r3s72hy0ufxudlz4fqu3x5jv npub1g8henaumhfjngrkpp7g7urz420hdzcx2hnh9grf2r7g3sxtur6es8uucpq npub187c8yedmqmss7fxtzqya4vphfkazl04lvrz7cp5xghhwzjduc4rqkcwd0t npub1vg9lk42rxugcdd4n667uy8gmvgfjp530n2307q9s93xuce3r7vzsel8885 npub1nkl720g0fuvzt4dqm5xxjet2lnm95z5fv4k3jvgz5jhnvhe2lehs98d9kr npub1l74p0yq6uzce4v4ntvvj9zcx03rc75g8gn0ajsccxzwyunv9m6tqwjlh45 npub1tl2pwveluev0jcmm973x87qt0uy20hxnyrcwefxv3nkv9kpxmzgs5pl9th npub18zhn7vrv94vy26vsf677uyxxvs29t2da492xs3xnxl45sszvh5psw9vpuv npub18z4uprsemsf4tcxdnfc8q2esk36g5rleqp6mw9ealtn2kmv8pxjswswrvz npub1wl8u4wfqsdz5m9ey0vvzh4y05mcpk2lm2xhhpw3uzs3878c2mw9sr2ksxk npub1ejp9v82302mth0k3nlanyh4zm4tskvg9yk2hp5fjun0g7uc47n0s0q07vf npub103wzz5eeegcwzrchje02m4rcxqxqtz2rauefhdshmtzd9xjxxdnqm5kd9u npub1k9mx4t56d6jsm658mmnwv7uvxl9edflkelpu4llgwrlc220d9qlqcyhueq npub10x8de2sz6apxnju8wwtqx00sjkeqj22kcjjfajsa9hj77492hkhs4g287f npub1q24ugzmm8ptkyq3gwukkl680kyftmlk3cmqu49x7yy4zuv94a3cqlhw8ld npub13xd3wejhu3xy5hmzgd0ymc9apee7ett6my4xsug5ya0z2f650n4qaf9f8z npub1vxd0dfst8ljvwva2egrpc53ve8ru78v8aaxfpravchkexmfmmu3sqnrs50 npub1nnyqvvr992hn3umzgehppzt49vhm9u4vet9zhzks4wq2a34ehv6qm6wkx8 npub1467z25r4x9xj6xgrgsk6a9gytdy0qp8xuupplxyunzfp5esk2uys4gm0a7 npub1w48530djsgja5d63k27mr8krx3xg63qvrjhczfwqgtmml4kgxw3qpcfwvj npub1ymldfnyvl2u5efjkdlqhpjruhv345qtesj9jf22paxmgj50nfxes3k4wqd npub1mqn5acr09lls33wapadkdf27t9v87h22jf53c473wzpkgld6z7hs72mwzd npub1y7yvamgvwdt6h8skh5yf5phn25yt7c6qcpclgpd0nglsy3f5uu2qu47fad npub1q5jxvccuds9wmpqhr7p770y4ewqcfr2dehqarm5alhm4hpgvrj6qtm2qhm npub17nd4yu9anyd3004pumgrtazaacujjxwzj36thtqsxskjy0r5urgqf6950x npub1k2teldhmj7d53732ekcs5ta0qpjsj9fhwc2e5ve5wljqpxht5mfstxx3qw npub1cn4t4cd78nm900qc2hhqte5aa8c9njm6qkfzw95tszufwcwtcnsq7g3vle npub12xm5ax6rqp3n9n0lwlja22lpfuwc6g63a76p5kdxuszqnn4ut2ssj2k7jn npub170d8w0jjdcjuh70lq5ppr0pcy7cfuxj6hpr00tm4et3v53j8pvrqj0chu7 npub1fs3n5u75kmtfgzzuy5ms5qexchv7kz3altj7e2uzl79ygf2nn0nsv2sdjg npub1y8hsmp2pxadwf09g22zsjla6xu8hu4qttgcwte6kwrqkv70e69zqvtfqyr npub1rtjk5n3cgdepj95wylpy4h6etg2jel3erpn8px9wxys8tuueeeushu5jyg npub1m0lr5fdjrhhwxl7dev4h7c5yvruz2vp949tun5zmulxuktcm0fusy0gg5r npub1ur6emzgy0wrg5xyvtm7khy7a3sttv4jrhpcc3px6mp2z8pkxphwsyy6kg3 npub1efyfeevwrtxnmncs8767p66wxwulm0wd85cszksw6n6uw2qtca6qzfvgyx npub154efugcrxmttmnp5cfxpnhgwglvxswsxh6d84jcj0a865a7s4jgsrrun7f npub16erzcypvccc08a6z6l6gw830zj7m743ah3gtc85rcjhfqmqjccksce7jej npub1jpxn8d3x0p8cdxvxzafpcpqwsfnvgntywhgne9w085fzu2mjjw7qldgdg0 npub165llzjv9ux2s3ezx5k6l4mzhvly9n8gyzhx5p7v4499heee4w4fsvhnu5w npub1mcgm982av268z989lv9h23f0w733wxecqhjjw5l4dvzdjgl0gu8sdss2v5 npub1z3adf0m2c2mul0vtpru4f5uzghn746xyf2udxv63de2ckcmg697qqmjnvn npub1520n32u3r68qtlw5nykxegtxkdt09rpk7h52laectc4qvdcde34s2u9qsw npub122fgydglyvhzr753e0l6k092x8h5k4ev0g9v90lpgje597srk6gs420cc3 npub1xngvle6vzkusezsxs35kgulf6s0usjxej3qvs4kczezy6q0war5sxmumdn npub16umw99z8jm5r55neprqmvlrsqzwklernxnczam2xu5q5fwjaj2kqttgcvd npub12aa8fnjcp84epqtmhtnc4w2fah9tfyrews76nd8hqltpedf4l75s5x6lg8 npub12mllp29adf2fw0eeahmseczcu3y4625qyn3v4uwfvkpzlshnmj3qs903ju npub1l8qw5av3039qhefprytlm7fg8kyyc0luy8yk2prk2l8wc38gf86qzw7nnm npub1nwrrty92erpe8th9wv4u9l9f20pqqh872kwjmejc6mu9hfnzumfqk5fua4 npub13qhkp54f8w0vgql3lqukvk9pduhef099hx0azmzupuhxevjayy9qsfg266 npub12jyfh0sy02ku5p3zg6hhfvph4zphl3y5jqfk9skaqa59z7pmfh0qqyn9mn npub1t8pha5vxkct4mlhskzz4pshvwznsma5646nmzz5gcth06mth0hfsuleyrc npub17ptx9z8mnyw2vd8as0nyh40gtvyydufme8peweh72ax9kpxrqzxqmnsxpq npub1lzh4pgufkx4xq675fujac9mmxs5zmf8ffucetgp02vep5eae3acqwez9kx npub1gnrfjvjmu3jucpmkvj6ptmdxcj766hwcrekjeuzlwtcqrqmyszvs3pr7lj npub1gazxqfx8ldqkgaldz3hlwed2h3nwzfmwavkxp3s9j36qhfzeladsmfe0a3 npub1xc5c7srsajcem7s8x0sndqsu6yqe36xzu2kdnu0cky353x6tkreqx4lsgg npub17kytlyvd28tvpz9u8z2mrr3pq503pmvtv46qskjccfch9vwqhadsregenj npub1vcq8nv3lctr8ctk2dp7h3e0su4f7gklgx4dlm2375l6u69hvuh6syj3d9l npub1v6xa5avwqkyqwzmfhu0ul4cm892txq4jnxmxsvgt5pnralqj9upsnmsnu4 npub1m986jhedeq7xxe8ukxc3dqwqzcz0ue9fra6m0t2zpvp8yezkeexscz7ena npub1yftkt6shs2fls0djxzww2nc7t96x6uxq490qw860ssfda755pc0q6emnz3 npub1rl5s8caaq8vsjfhxnmmmguxryug2f2has0kg5gzedepzle8quncqn9patu npub1ucsl4dgwslalsgje4es7jefqexlsf678wrhvu8q59e3djzgl7krqf2hnad npub1hvzkl03x7z8fews3cc5h99mxtze83rwxunre2687hcdy0zqn0cssnszrkx npub1q884swxynxp5dt467g0v3gk6t89tgd3r90pgdwcvxtlnjf2l3jtswgwvcc npub169jj88ry88e7f6cmcngcz8mu67ak6q6u2pgtcae6wa4ju00z8gts8hac60 npub1ahfkmjuzqcngqule5c4eq3cucxd65dpkp0sguzzsr2duxwlx9guq86x8en npub14xcy30kssvtpj29f40rk2kk5d2heumaxnz77ahkuejwepqngy9nsewgz0e npub13jpmntdr2k04x76f0c76syf3za42esn2nnd6kumc2cwyltmtje0se6mvqj npub1us9tzl0zc0ggfqw6348wyctck7mmh34w0hpn2rs236akusx7ltjq5s8gtq npub1eykpylvevzagq8jm8jutf2pmjnnelmyuc56a66v9g7ttcth5kfsq6vllrz npub14r294afl5jqgvj4hlfpj3dvyxenxh4vuhepn68zdurcas5r5xy2q5ydufe npub14n46ruge3mmv72xeyjw5zl4cec6dykrme78plmm0zmpnclcptqzq7kct5u npub1yvw87p6d2rmd3lqdp3c6npjhunpra9huxnl8c30rxjw8tnwd292s3jusa9 npub10agmu2vwed988jdxs8cewppw5jvk0xtvh9vdyguttuhugu930fdsdcsdp4 npub1gyu3h0kmqmecf6044q5r88vu5vtf5u6rekh9yazxrtejfexct0lq5zpudc npub1kstv7m2flm703dmufltz4l4lkm3pptl0zdqjvkx8ap3aagttkd4s8d5pa8 npub1rc56x0ek0dd303eph523g3chm0wmrs5wdk6vs0ehd0m5fn8t7y4sqra3tk npub1mlf37lk424pxrstpdhxqp04v637kjyashaj4ea73gfz86yr4gdzq3mjtav npub177xlld4katf3aardam7qpu88l0ttvyde739qcvjdjynweqnncuqqvxmfdc npub1ykfmyfwtanmhvp06wn3ggwm0gl0v5v2ftmnkmhz6swl2x4ur9udq7ld2fy npub1a5pl548ps6qdkpzpmlgkhnmh2hpntpk2gk3nee08e5spp5wzr3qqk7glwn npub19gskj4eqgjgjrwjw5zhu9rddnrqfq59slm5fa5a9crun9wm2qlyqccyh6h npub1ujxurwzpfrxsprf0urqfxpp0qpm2yrpneat4udg7e0v560nzw3asml0d9z npub1ep6wcd256kvsdxey2ylycrpvmf9wnsqvg46kzqrhuw2akxj020kqvkq9hc npub1pumdyz7qfu0suamv4nrl0vcg574dtl5mwazva6nyjxhpwc4ccxxqca3ane npub147d47sem878zwqln7k9y8y3273v29ase4r7lk5yeta62xk3t739qu5n8zd npub18jzu9qrrmhhwk57zqhfffymy7hq8vrncxnvl0sutu5y2lhr456sssgsesp npub1wmnvcv3ycqmtfsysmrnkyckja8dc9nt5sgf60rrel339v8chtgnq4p5w26 npub1tc07sk67d2rs8x90fpg9x727ulzknw7xjyk4lds7pkzauw2tqntqpzs9dq npub15h8pr8t0l6ya275k42cwwhrfu6z6vk6qydkdn55p6wn4f424s2qsasdczc npub1l0j7srkgmdwy8839st2hn8f9utlgh9vtrm04jksh8tsu32h5vpms9k7zqa npub1p9auvqfn3dtrjnwkhxdvvk6xn3tt8aa2uv4dh2af42nv9z8nh0msrjvmhp npub1lnjp9d8xz5zguufe257vtx59kgjuxxufv0fjnplwcfncvpc7vahscraxv3 npub1mhp87q9axdlwh9ac3p7drg9z764mxwe27xvxm7x704l9dykfy9xqrgmxdq npub1253ehcqxctt4ps8kjfmhqje965v8gtzn7c6gtq02c3kqvtxmsx4qv9my05 npub1gk0yyk54t6ptq5m7hygy8rvc98pq9zz5uhusz9ht6yxcpmvsr59qg5ptts npub1828ey4s37t3dlwjmgsa05zafvdlsfsa3lu5vlk5cdx0a3zppv7nq987tnk npub1h6h3jwx3fvz9sanmg5yx6rutmggsnz5t09t795yf4jk4dqsfyq3q47kcxr npub1cw2epa68jpmy384t7vn0suvd3mxnk5s02ap6fcwg0x6jqy4lhdpsfg84uq npub172g2zwq6vkerg02urweyt2daa0huavn6ghcr4gxt93lmhvnzan0snuwkc7 npub1awwrv77yu0x9rvuaq55ppntc52rhxt0w9t32zkyw2jszvmgsqnkq2f3lpm npub12p25mnqkunnhup0sk6ky0vvtq5pnkapezx8kh689dv2vl2wnp2vquyfw5s npub106yj5wlntf5els6w5cw3gwmsgh4yu7vs0lrpw4c0uzkq3rqmkkgqg7rgpe npub1a4u7yc39v6fvr48a3skz9gwdzl76hf499mk96x703nzc23mdqq2qe84e0k npub1fc72tcwhr5fhcmcczzld6femwd7d7uhqwjw8rp5w9enxj52xjqxsmpgv04 npub14h5r077z3edgts6wl2me5vk52x5se6nnhry0ldfzua872ggcxw9slkd3fd npub1xlngepdt5qz752x9423gnvj2gk92j55qsdhm7mrtmju7x36pwnxqg4sypx npub1rl9wszqmsqduzjagewq302qfadjy4mt5vw5zvm8xdamvp3d0nm3sr88s7e npub1ayvrrlpygam2ruyx2lhtkvgjc53wjd3vvvs0ysjqh3pwhryaju7qd60eq3 npub143mkh6lvtrha7w7pjw32ujkljc9ell9wpyvd707nahqy0rt62kws4wlyhl npub157rwfe8a4gffdcx5ca56q2qsvpp3z757674lkwca5ud9j9pdcnaqct6p2h npub12z3w5jynqn3pjt73kqz6wkueygrvt57qfwgxy5u5pmn0uqutdwdq5jpd8w npub1zfrc4u0dnph8flpqar5r5lv3gpn7qafhlh35zpcm8e6ex4k24snqhx69js npub1rvww8nakj7rgz59jdqlswdmvjn0cd46q2h4y00wuaquwyn383fysxlpyxt npub12knmfzy88xpc4dhuly50tlhcnar07c4pd3w9pfpd4lnssmwhvtrsgq2ez4 npub1705am22u3tep8vvdwkqex0jm9pazhmqqyxvaqzcnv76m53xed0xqeetuva npub1q0k8epddegnec4kj0j3rew9yel0jsrp82sd2new0zy3m9pcfgqas4r5yp7 npub1fcj3en06ajdm09y3twytsrnd9n7yqayt9e9xuutqdrwnqu85t6nqt7rz5p npub1jvej78jr00s94gdyct9md9x2ljtjr0jhej5c4mm7cejp39dwgu6slkmju6 npub1mp0jgd4gaj5hhw99lfwxufl0k50m398jcneqsp940sjzz32skmzqw5uuat npub13u8pyc0azav54a9gg0py5khrmd8er6ac55kvag72h43r4q8s7nnqsqsy4t npub1ajan43fcllaxc589juls8pef90cgdya0p0en38h55fal42nlgkrsvltfdv npub1pvn0tyrrrv86xpydzq6ppeyyuh3zut263m82emdfmydn37qa6x5qmh8khc npub1pfx4fj43y5j27ywgj02axnyup0eujtk3g6r4ug2n4nvfsa2kpl0qwvtah5 npub1rpx2y7u00jmsvwt8zlkztajmk3e5se89vhnswsz4suuyg4a3fx2ses6lkk npub10jhpwcdsc6mrfs8audcdds2x5txdagru9835f3drthzaumxurduq6esrnm npub1narc0ect9jf0ffnvcwg8kdqlte69yxfcxgxwaq35eygw42t3jqvq4hxv0r npub1yrffsyxk5hujkpz6mcpwhwkujqmdwswvdp4sqs2ug26zxmly45hsfpn8p0 npub10ua5vjul7d3rvvzg2psvhk36w7gpx8zn8xncqw773l4hnf0pkp4qccymjg npub14fzrwpygf69t0e9snrk2ms7ltn8u4dnvunl6d98zkrgdzf256exqa3j6rj npub1x8vkne5rx99wzup65m7gpmhmgsa80d3dscp8hafrwj70zxzkyexqttjd5x npub1643y7m94wwu30awq5djh7lkqj48evpz944yetgzhssmykkh93zlsz22hhs npub15pkupvdv7hmcjumlrx5yjmcwy2f9fl9fmsa9mx7qjlau8k59rxusq2v0ny npub15wnjy9pfx5xm9w2mjqezyhdgthw3ty4ydmnnamtmhvfmzl9x8css6kt8fs npub1saygqd4rdf8edlm3r45cexr97zndj3254lxyz9dejjlztscvndcqhcky0f npub14neap59th00w9keu9uffpal72dxyex5u7vc8pwsuqrdxes2mkrascnlukg npub1nyzep3atafwfrnq7346dmx7kjhqsrza936rnvnlkv25fzd09gxpqw3gg6v npub1chgzxyqjnvv7ryuf095cswtym37jummaqme42dfez8q25h4l734s9xdl08 npub1gp0cpreej8amtmmd4zn72hvgr4d4tgdhg3vpe0m4yxzqz7skg5eq47jmuc npub10gp3mv09aet40plum7f4pllyc8g8u4thq8mkkwymdcct3schagvq6fuh49 npub143jqpdq583jd7t4ucfkr9wzug9h3904vcng0vymyley0dx43vv8ssk2gc7 npub1z8y57drslgthaefkvya7kmqcdm9c20uutz336j9hp4frkrg32nwq9g4ju8 npub12er2cnsfzc3d5ceggpjazwx9a5cwna4atxslkwe8975lp3fuy6gs6s36tk npub1cpxjrlnhfmcclcsly5c0dvrgvl5nsctzxpp4s9f2nh4qeq50mwsq4089fc npub17dhclpvjmlkhlgkh04sc2296wj0veae79fq8dkwr5efvlz6vt79qgyqztn npub1gm7vxd6yjqsjx49ddqgyflllpjuhduqch79jlp07upsh3uf6q47qsm4xlv npub1d8h26etwdx6ws4afflra7reqwtvjsm7u8zn7jz0w5q0ah4tgx3rsga3axt npub18trgdajss33u25jvk0g2yv6lxr7s7k2dlkkku6eqq7m4hrc6aazshusdhj npub17s290m08ukaz9j3nhyuj5w2zyxtdzdqvrvsgv65c7ckcxshjrxrs6wnfhy npub1jlu3zyj7f2hacdrrmy7jpny9f7nnvuxt2flrasjtmgut90502xqqtsx4rf npub1vwcy6na4rcx6r43fqyxkhzzdvqufctnx06ywvrnajmq9p3mu27yqxy04ch npub1ea35pc7pqg2uvstspd0ljlu09t580qc942n5eevvmkrv6huchffspl8087 npub1jxl2tnvnv9gycsy64aze295c3a529lx5sfmzlktf5lxuw805g5wqew0z0n npub1l885a986vy3sj3watelhdwea74jxhy8688ju4h2c8wz2e94tcd2sl7qjy9 npub1uy7tnhwxsr0tc8eexksandgcct5wtua2xazvl2gfyy5n86p9sdvq7nwdzc npub12wm6zfgan2v2jc5tknkjsj9d64qfk6y4ggu32f9tgnu0mpuz26uqctkvly npub19hvj2zeg7ck8cj2p2az5y0gplllhgzzdu0khu5fhnpfmum5jspeqqcdjej npub1cqykgt4enf0ce9v36kjzugx94l6tp8dd5k8ktfgga9ahgs2mzess82r6sm npub1th77tvx7c3l9qgxql4grcllh9qahyfvz65ruplrf6kh0sfzuya0stmendl npub1w98zr2sevkqle6lmt7u503ewclhzs2cdq94ke4mw7kmpxy2u9y5s6fe9yy npub1c999aq8sl4fmw8an6hfj5lfhuneqc35seffqs6938hxajr2jq6rquyvp6l npub13tnrml3s46xswsk8l2p4tv8cdmnpkvrk4p32828jwce7puefc0kq8jlf2d npub126v86pztd6emjtkwxe8jj8sa8f0m9wcavsd4j0raemdxksegfg3qfaan6r npub1uz9f979gqjj0ymul0kqq79g8gtelwe6rs276jm7qnaffmn545h7suw6nhl npub165h57grx6hjw0grfcw805srfxl53ggcsl3mmhagmp7rg8x80ehasytgw9y npub1re764kr23sa6d2ld6fhukthcwgnwvsrahe92zq42kpdu3lm05sjqwjchtt npub1m0l0harjth9sses5h0r2slf7l4wws4clgt88s6n23ct2kd2xdkusf8nqjj npub1a8w23gjnfv0f0qzjpfeqg7yc5ddf4c8m8jks50l84lrv7h52jhgqq734am npub178p8fw0spjry5824n5wv96rfre8lq4r30ysyctfspzy97n3tl0nqcg5hzj npub1yhyc5znlka36gx496q2lmqhyttlef7lpkx790vjmsh2xfacdeu6q9zu2sd npub1h7mp8nd39hzxywqdl28rm2du9j2jhcarmsmakmulm6z7fc4lx6eqqaxh7q npub1dvqg5278etemtvxl59ahcey8cywrcl0krhpu8dt9s70mgwjar3jsqh5ywp npub1dpm87jq8zpgrvq2thr80chmjjrj0tww7q3hx9kq7wpzq2aayqxdq9a76um npub1l506tlst4adydg0tkshynjw6dsk5ukjvpzr67y9vas8v3nzxylssq6p0j5 npub1pe493zu4ax53pthcsfff7uehwppc9w6peashtyu972ey2szdeheqxcfk5k npub1kuxfh7e9fds89qzzzfjrh6c80d46jstqnm2q29wekyykr4mk0zvss3yn27 npub1gwx22vu2yzm8eq95nvvmgvpax04u96gq4r8rgqqf9pgsheu2lz4q429cus npub1n8ahhlw8trcpwkqdcetl5pgqvrxcfvgrtj037zlflrnqymq5f40qhnwpd9 npub1ujr9zwz8h7xtkvp4pn6aslguqvks43h8ej2z2g86snff0h4xxmuqjzcwy7 npub1vm4s0uqkydaqzt44dyt38p5spltl6637sxrfxswmr6k883f5a0ds8taxyl npub1zqvtnvxrdpg5vwh5alpx0m567092m2ltynqxlk004976tgc6syqsg9rcv4 npub1ld5xqfflwy6txghaaef2d4rnyzkvwvz2crncmtvhq93xxsqvzqtqzdx4yp npub1er2xa679095y03xlcmycgg4r93nluqpluye44h0ndxdy6k5uxcdsqwtqkf npub16jde9ylpry7pyau6svgqktdes242ynfk9snfafh8gq3r3fj5xfus44xm32 npub1zqgjtt2ayahsuxzp3cg7h8qwt6ev7phz9x02ktc0gdlwz70n23nsla0sph npub1h9c96qqmcupyvtq30d0xvp97h2cx966gz8n55cqgd24hgzvz047s6hxyd4 npub1h955atshn3faxg5r40p4achtxg3q832h0agjn24sf63tnkg5ezfq0fnr0n npub1ker60jkxmxjmft468v5wzth5757v2end6wzd4xn67jyej8taj4zsyp7tqy npub1ddjzjva20mwp9xals7v0nh3devvjewevkkrqrsglyhnwa59ctswq6kzdys npub1wtvrnst9hus9pvz3m95pusfjzq4z5zly3w4lehulh6xc8dajl60qsrjg5a npub1hl07ukzg0xk7gj6ejr5k5e6gmakt9tnu5r07f543ce6e7sa7dc0qv0kcun npub16dana9qsfpf48ccyqwvl8jlw6k5u8adly9ph76z0ftrs88lf7vtsrzlu5s npub1fyd0awkakq4aap70ual7mtlszjle9krffgwnsrkyua2frzmysd8qjj8gvg npub1saessfmtu5xwnwh60e0rwnj0e067npv6yxgc7d96algqqart056s5gkuqh npub1lylzl87mst3swjtj97j8aajyfmaqctaylgw9et5agyp3rl42y5as87k86d npub1z324cpkjv9ay5fanw7rex5847dy7h3ndvaej2hy2vmc7r8c35res3x2kje npub13zlwh0n00pja6dkw6htamu6sl8668hpgr45y5lnmnmvt92g3laysqqsatw npub1u2ukfds6k42qwufd9xd5l535lxt3g2zet9rmmlhagtjxg6t8e6asmx0w6c npub1ezeah83hkpsguazn70rmkmfwh864wdejv7h7q7tsuq46wquelelqu8fr7h npub1pvuu3ms6vlu7lmysggjuuz6ctsuyjdmy3uhlywg7jxdewvtr7rgqakhnsl npub1vny9x6jl2cmvhva8m9gq05z0vf2tar3vy72503hvuru0pxtnz2vq9v0fyg npub1s9s55cwl2m6cd5czukune4y02gecrn7m2tukj8zt4epheaqlk7wqsd753t npub1qvwpwvdvq4hckarg9ekldnvzza0shka85fk24uuh606vhg4l2grsuw808l npub15ksrns0fw4l8heral0hst3szmvpka67a94xxjcm3ddlpx7hcn7eqhwfkrd npub1zkrdvkmnx0sv7d8hyd0ma22lfvvphhd33d0qs3sg7lrtrv0xdv9sa7gy52 npub1nknxhegrddacazt8sax6cr2h0r9sht6ajmq3s82vjhg54ey2rfhsumhe3c npub107swly8y0ert2upsevqk8fqw9tvacfvuygw55qcv4s2eav6f0axslhmymt npub1a9a2l7jqqxa9mwrw034lcnuhcsncg905sl03ava49md55t4awewsvvzz87 npub1yudjcmkasasju6znprl3rpyp39xa3uk4g6sfrv3wxestqsehs3eq7z5f8r npub1cy3a6gug0t4jrl8plq393cjjxwtg6cewcuek0n0hkww4h567dnts0ft0dy npub19jxz6jynvhlwzmfyhmn5tzymdff0zuq8jkg2mq268a5045f6favswaxu2q npub1uvx00x8svjwma2zhddwpthyke6zc3rrxqg5gj8mxdjv77zvwmz2qgw603z npub1ewe3r7x8qemdh7v30gndpamgrmu0k6nu4twyt62r6ukvkvmpgkls24272j npub1deexjnst5g52wh9kmqr4hy3wzhh0gspujs2nc6m0l892rzj788uq5gcpq2 npub16qsq63pgxyw5vz6847y9w4cau0fmvhykw7uy04p50u5muulc6kwqn706mz npub12cfje6nl2nuxplcqfvhg7ljt89fmpj0n0fd24zxsukja5qm9wmtqd7y76c npub1nu0yladm9rr6wsz8w3v995gcxl88vqcdnp8uv3zp3xk978d3658s8kvmhm npub1dn5cj3n85c085yqry7wle93uhrqtkf9m2zwqgt8c233js0lt9ugsdr7zzt npub1vudm0xsx4cv3zkvvq7k5836tnkv64q0h7uudnwujr4a4l9zc2p9s0x8url npub12c68tkshmelhtrd7ye5fqg3gwttd33ly7gzxkwh2u4qt008nu7gstf7x0p npub1dc9p7jzjhj86g2uqgltq4qvnpkyfqn9r72kdlddcgyat3j05gnjsgjc8rz npub1dmqa9kg8nke7fc88p760zd8crrqupl4w5lflhgs0jgh4n3slmdjsql67zc npub13q2vzsfemle9cpxj875tz0vcwqe6r8sy05fd62jcd3xuxjeqj6ksze4xl8 npub16merj2xt59t43djfx8vf4fzhc6nd4v9hlsv8ej8xfl3327yr3vzqu8zjt4 npub15dqlghlewk84wz3pkqqvzl2w2w36f97g89ljds8x6c094nlu02vqjllm5m npub1kqnfgpzt3jxh69ma394r0azyurd6h3dehpw7lzvl0vv3n7kv4a0s3305z2 npub1g6jjgu06nctv74e96u84jux6vxm3ezncjh7tyquvm66jug02xvzqmqu08l npub1efk5xdyrs6e4lqfm7crut2ssdnhu54d9egswq6smt62v0llj37vsprp0r9 npub1j2gc7kt42rwf5q37dmm2k29rqxscdqt2vyfn0xgju32v329jfpdqmkq0xk npub15lymwv6mdpdc3j8zxf3qzq33j2lyntst9v83ukqpa0tzkdtae28sgef05j npub189ts86gs5xw5w2mcz0na5vkz4cseam7jnkjwwqswrj56v9x776lshjqa8m npub1cgf0yeja9tlkfq248l09hkf4kfjfyaup50laen46ucv8gf0puy0qlpxlh5 npub15r0z9mrt0nxzq5fzxysqusm32r9krljq8gh55xnavdyllk6gdxjsj36uc5 npub1qa0lj0jktem67zaazrvpgrf23qdcj3cw9u6j5ct55mg447tqnftshv420v npub1yxfjljjd3apsrvzlkww525jfvdsvuwcs3n23wpmy2txtsppzvmtsgxur33 npub1gv8juwhat4xkl734q684n6vvv8sn5k2dvm8a0wnckyw50zajdvhse8rd3j npub14tj8zkwatnjq4rlnruj53676thre3uss9tg8e23a6w4ewuzus60qe4qg6r npub1ylf8w68g5dkfqwjpdvsy42d2cwqnajswrhz323chsc7gnz400chqfmzdm5 npub1rhgqj4urjf5uw9y3npnvvst2hhmcdqghd26fzwgc4s5ptkq24d4s2525ja npub1lzmdnlsaysc5m040q5q8nlgmquldtxzgllegsg6z2n0engaxwp8szsswed npub1vr3860267yxktugg5q034j9xh3xjaxnlawvas6wqa5kw6zxhgcdq6u2yzr npub1q6ygq585gcs2m6egv67yv3a036jhry8zu93wk2uk68e3smdafl5q4sl54r npub1vy0g338hw6w6rn2fsv5s92nx47u6gle8v50ypxwj6k2hsj9p344s95e8r5 npub14k0ws2m8f5jfrae4a7smtmwgx0quhhl58z4rpd8hs9ar8mlx78ys0seswh npub1qahmtyz5pr385kqmvxqf0a4004cx6ncvnj2829rvjf0rs5ujanhs2ssgvv npub18wamvs6p7dslshavd24kv2gy72e5jck9lgm3f3e3f8udja3ramcqvrzg6q npub1njtezc8lznuj5ws6yvz6x324lzn2ct907s8vlwnxqph30m0gqd0qvpvr07 npub1vgppgksgzs7je6xueqqvkpn4gqmcn3nl96famz34zfhqzq286mdqqmecmx npub1w6nj3y6wsv9kfjev4jjdghsg9ajcjq2gtec4qfpmgcmkzljl4yps8r0gwq npub10l6udyczpjzg4wcer9mje4zkcf2hhus8cswhycwaxfanepc7fz6s0q7u4a npub1cwevvvcurkfg5wjtnftret2j7ldv4lg3x35sty0pm546p6jx0g8q9fa055 npub1v5t0xmnrcap5rah8cm8mrqkp0rmuv4mslrlm3ldwkr39fzy56mas7wvr3f npub1w2vm583yvalnc02ngh6rxhn4ekp8m0xysmrzr6s7ufdwmu9r9qxsqdg0ng npub14va2v0yaprmt0nn0qk7ga6jujfk6pdrfwv0kxj76a5ymp8dfdy2s5ehfdd npub1ztdt0nvu8324tg40g4ts8d6englps8w6574zyq2gkdvcrx364y0qd9x9za npub15qskvuagmaznzc3pea7vxh0890ycfzxxdx537gef5wl6cunan3tsdkld4r npub10vmwytmy0pypy2c0f5zen8auvl7ku5dnk53vaw3ddplw2fl9r9wq4hmr5r npub1crqgm8qg9kplm9rlwfj7uxdzdtanq6rfu9unkt4ckd8r7fn7q36s0az8tt npub1x7fj44hzhjdcw2jwpylllpdgeh9yqqt7fg35ucfaywnw68tctv7qntw8qu npub1rj46xc5tssyk67ma9sslqqt90d597uuqx6v7tprv8alt9enk6v0qyvgn65 npub1y9a3x4e4zf6fu2w0cyyx9r2pmm6qtzrv4sallyznflamhplz3jyq0gq7gp npub1ukm78z9nzr0vnq7nqn8tvx95htttj2f48n99n9nqlky547rwzyrqk08am8 npub1p93m0semtesnsm2fjjd0p5kwl8gpwdqsnfq920zqyhfcc3j4nddsygyk5p npub1rgtl4ay7dcnud25enknv9230r3u5dmu3h3c7mj38jamrz4g3vf8qj5cszy npub19ajcupesc6zcpt0tlg6jv2l4w6wnpx985x735445fvla4w9zqqkss69s06 npub1kpyx8lxklwtd6n496rqgu8kq2k3yh2svlzr5sz3jlxlnphc6tcwq8kllrw npub1sg3qz6633ajzfg7w9ptmk0hf8ckl9jvv4zh6ttxt39jne36wnpnqyzk3vn npub1h5e0y6r2tagu4cygnfggzcfrt4afarvcvvcgqmpzyv605g4n89nqhlf2e2 npub1n6rffa4wqh3hcuurlf298dx8j59wxkmjth87adc7ektxnmpgxwgszk7scj npub17ml9y86nfg65h68pumfkclr3ay24pcfduu06j2jfp4pz2yjcpcjqv04fu3 npub1rkz86wjvey3vgdy2pau5ulpzdmxyzq4g8xp9cd3tu6kqmzpqcppseazx4s npub1c664gerrwlc3rlm6nnm73uc2kjyd0f7zaellshxyfdrludtmcf4q3adztu npub1zp0ys9ysfyrjvuxpwhvyevgphkmluynreun7fg2jeuu9xtsjwa4shlqhhn npub1fp0w2jd6e9l6pd3akr630d8gkcn39t2vep7u3ac5265fezu2fnvqjxpa2s npub1jz8k5nl4978lnhghlzeenp3nmfyvykqw5pjp620jj5qft8vqh44qp6pjk8 npub18vay956v7zs5qtgc65mvn54v96cuvqv6j9fmu4cgfjqkt5vjuvjsc47nzf npub1kgpnq8ycudaq8d7fym033hgdarz3ktvcws8nxt7p9rnfv98j7cdqftrga8 npub10wdzfpdpgyzxj8a4xtf5dux5z8065pan7xrcjh6gd6plj39qzycssepffr npub1ew3rlwvtmxw903gnqx92zar5dcyd47pjjure7ut2wngyz003ff8q0x0frx npub18urkgk8wrf0esedp8gy57670q5qxry22yce7rwrnvvrur736p3pspy6upf npub1pp8mxtdgamg65wfvrtp56v5lnyvv2kmx45cxd5m9dgcdjqqy5ysq5qasy3 npub1y5vlh9z98stts0rc5mlufellseuwjtyaa5jhewjqugnzdwt7yvgs0ydryw npub1gcxzte5zlkncx26j68ez60fzkvtkm9e0vrwdcvsjakxf9mu9qewqlfnj5z npub1x0r5gflnk2mn6h3c70nvnywpy2j46gzqwg6k7uw6fxswyz0md9qqnhshtn npub1lc6c4ukssmuf678py7k6thmlk8c4a52l9zx4thec48ve2qmcdqys22jt95 npub1h28yvj0mj692wpwruqdhyjngcfh4la7gaygrent6a3wwqjxcah7qnt92e7 npub16g85fanyh8sq48yjfq0smqm297yw76yxlcdvjq7hkuvm7xjjhn5saads2f npub1xc2plng44tlj2smv65e53sf3uaqf56c5gajktyu8zxn2p70jrxcq230nt9 npub15l8sfm30uwns8qrcajs99narc4ex65ujt5sky4zx3dpjhnnk2szsqu40n5 npub126u9v4tqg79hxx569wyq207q68j4vn4yme8he007kqfg36va8r8s4qvqs4 npub1stv2q4hwrk6ggvw3hxju8hjakly4ev9wt5tn8gnl9cpaqt8799yqj58ygn npub18yffjalmcfn4x0x0jpj3xm8g6vdx8rp2jd4dhnpr7e3xpemxlmas9w0q8u npub1wmmlxqv8l6aks90jvnetvwkk2hqd7pmqzk8hq6v0tkjrpqdvm8tq0exs5c npub1z8v0x60ukxsk00zz5s2uqgvlg6p8dhunnz3fn6wtnw48xg7p3wvsgmnduu npub1vukz6scwfq55vqjpv3z52theg0lwkrz6kncwc3rfkczl3ukafsfqfnw368 npub1kujyqe2m5w9895kfx7agwjag0xperd0efnxzfellux0xuj5es28q09lucn npub1j3tn5wdn82tmlgvcmhtm0fwzqpwx86pdgr3538rh7asdvkas2ktsqlnxpf npub1g7tavhda0yc8857nj22feuytgxskg4dlpfyql6r2d99egajrss7ssq730z npub1fsyfqrleejgdmck8rxd64wkhdefjthu6lgm8eg99r9xxsl9hespsnmfhvv npub1mevkncsv484u9nue4apgl6ue2644x4m57y9cmztnvwpvs0tnduysg3vdsw npub1a2mj00469ng4xy87nucds99e7m5djh4pe3rpluvhcnaat48gpeysj0gy8v npub1ggfzdxa8xrrzhaut6venkrmjtw8wl25y6l0wramkc7d4dlyaflzsxxrfcq npub1f945c6sqw2d2aqktvjrjtu9uca9wdd6ua5e0a560jak90rr5ha0q3tj4cx npub1x3j34yuj6d9ln5ryuw0ncy97aa6ttc5wwyxqwvjrz7mg039t6l5qd4ewrm npub1d0jucp5jqt799kjuqxzs4cj377tew43dpcr60fzyvcltc5jemtcqryyvcy npub1m6keqpkqfp0uzxdzm2q0rdw6pzxuln98rzla0zzywwdzgcyw2rpq56p4d8 npub1p8ymvhgtsyhyqk4y35xlup20trde4pa69pxf45hdxc74zdkyhfvq3narwh npub17n7fe8p607xgzj2hzft5dsqvsus7mm3y0ceq0ta9a30s9akatq5sqh9y58 npub1he7j4yt7ad6kd07ynqk9qmhfqflw642qkjagqvn2eektqrl90fcs6dlraq npub1mryqu5cffjqpyykvmfjx3js8j0m0850v56dx24lhyqgf2uhl5npsk9xj7y npub17natddjkmse4z8frh7ysynwtzanzmvs9d76c5r53546wsnzs25gqfdeqey npub1ywcw97xsl93l0mqmdpshqx4yu507xqa8zy8p3l8vrkgkek90wm7qjhp74e npub1d9f66fpawpeyrdh9jkyccfdgut6u9ghufwly5gyttfy790mp88sqgx5v98 npub1cx5js2ma5gf7fqn7yv8sjtezvg3agfth7yyxhwywtqypkat493ksjm7yr8 npub1ykrmhyqc0mjhdf5mzuz37g3jkt5ma7v0uesmuyvhueaqs5ysfres02hqjd npub13k3ynlhc2ret9nvzamj4cgrnq9fx3uzyx8ral84tjtk5pmxqpcysdzrzgt npub1jdaa64eyuql4hd0244mp7z7n82egpmt2d79ny9avjufkpm5gz46shcdfng npub1ne99yarta29qxnsp0ssp6cpnnqmtwl8cvklenfcsg2fantuvf0zqmpxjxk npub1klwact0ar00r9uer7tzh2zq0ytx3f552tt8qavszdhvu6vpv3uzqwpkjqz npub124rja8qp7dartasr9wdh3kk78phxunzhmq8ar5ryd2anj2qwtcnsz3tuhs npub1c7kdmhhae7x40q8zq9eudgqm9wgz0q3av4nrgaqe2qqphqmqvczqhee447
-
 @ 662f9bff:8960f6b2
2025-05-16 19:57:46
@ 662f9bff:8960f6b2
2025-05-16 19:57:46Let's start with some important foundational thinking - based on natural law. Money should be separate from the State - if not history shows that governments and human greed will always take over and manipulate the system in their favour and the expense of their populations. For extensive references, read The Sovereign Individual and The Creature from Jeckyll Island.
-
The Separation of State and Money is the most important thing you can listen to this week. Thanks to Allen Farrington - his paper is here for those who prefer to read. Wake up, folks!
-
The American Forefathers knew this when the wrote the American Constitution. Thomas Jefferson said: “If the American people ever allow private banks to control the issue of their currency first by inflation then by deflation the banks and corporations that will grow up around them will deprive the people of all property until their children wake up homeless on the continent their Fathers conquered... I believe that banking institutions are more dangerous to our liberties than standing armies... The issuing power should be taken from the banks and restored to the people to whom it properly belongs.” Mark Moss explains it well here. Charlie Robinsons take here.
The situation in Canada exemplifies the issues
Governments have have long used "international economic sanctions" against other nations to enforce their positions. Now in Canada, and soon in your country too, they are applying such sanctions their own citizens - disconnecting them from the financial system and removing their ability to use their own life savings as they wish. Canadians spoke with their money - in one week they raised more money in support of the truckers for peaceful protest than were raised in support of all Canadian political parties in the election of last year - only to have it confiscated and blocked by those politicians.
-
CPL. Daniel Bulford (Justin Trudeau's body guard) is particularly clear and eloquent - https://www.facebook.com/watch/?v=3123688351279364
-
Nick & Greg (two Canadians in Canada) explain the situation to Peter McCormack - https://youtu.be/QBWYp-cBr4o
-
Dr Jordan Peterson and Dr Julie Ponesse (also Canadians in Canada) speak openly about what is going on https://t.co/2T7A4VEek1
-
Even Canadians living in China speak up: https://www.youtube.com/watch?v=xvDvJWdlD1E
Meanwhile in Turkey...
Joe Blogs has been giving blow by blow updates of the deteriorating sitation over the last weeks. What is happening to Turkey will come to many countries - sooner than you might imagine. Watch and learn here, here and here - more on his channel.
EU Citizens should be aware and lobby their MPs
Dropping of all C-19 restrictions is a tactic to stop people thinking about them; meanwhile the politicians are taking steps to get all of the emergency restrictions codified into normal law so that they can be deployed on you any time or all the time in future.\ Act now - or lose all freedoms - your choice - watch here or click below for the explainer.
More on war - recall our discussion last week
War steals and destroys the wealth of generations. We have been here before - remember World Wars 1 and 2...
-
Dr Mattias Desmet explains how mass formation psychosis happens and how he became aware: https://www.youtube.com/watch?v=CRo-ieBEw-8
-
Be aware of this well known and much abused psycholgical experiment - rats in a cage - explained by Dr Christ Martensen: https://www.youtube.com/watch?v=7kSBdMXQkPI
To remain silent is wrong - to deny the rights of others to discuss and challenge (and even to punish or coerce them) is a crime in support of the biger crime. Each of us has a choice - choose wisely.
Could you have known about this?
"The Matrix is a system, Neo. That system is our enemy. But when you're inside, you look around, what do you see? Businessmen, teachers, lawyers, carpenters. The very minds of the people we are trying to save. But until we do, these people are still a part of that system and that makes them our enemy. You have to understand, most of these people are not ready to be unplugged. And many of them are so inert, so hopelessly dependent on the system that they will fight to protect it."
"Unfortunately, no one can be told what the Matrix is. You have to see it for yourself."
A closing thought...
Look closely at the cover of the Economist magazine *released in December 2018 *- The World in 2019 - see how many of those things have already come true.
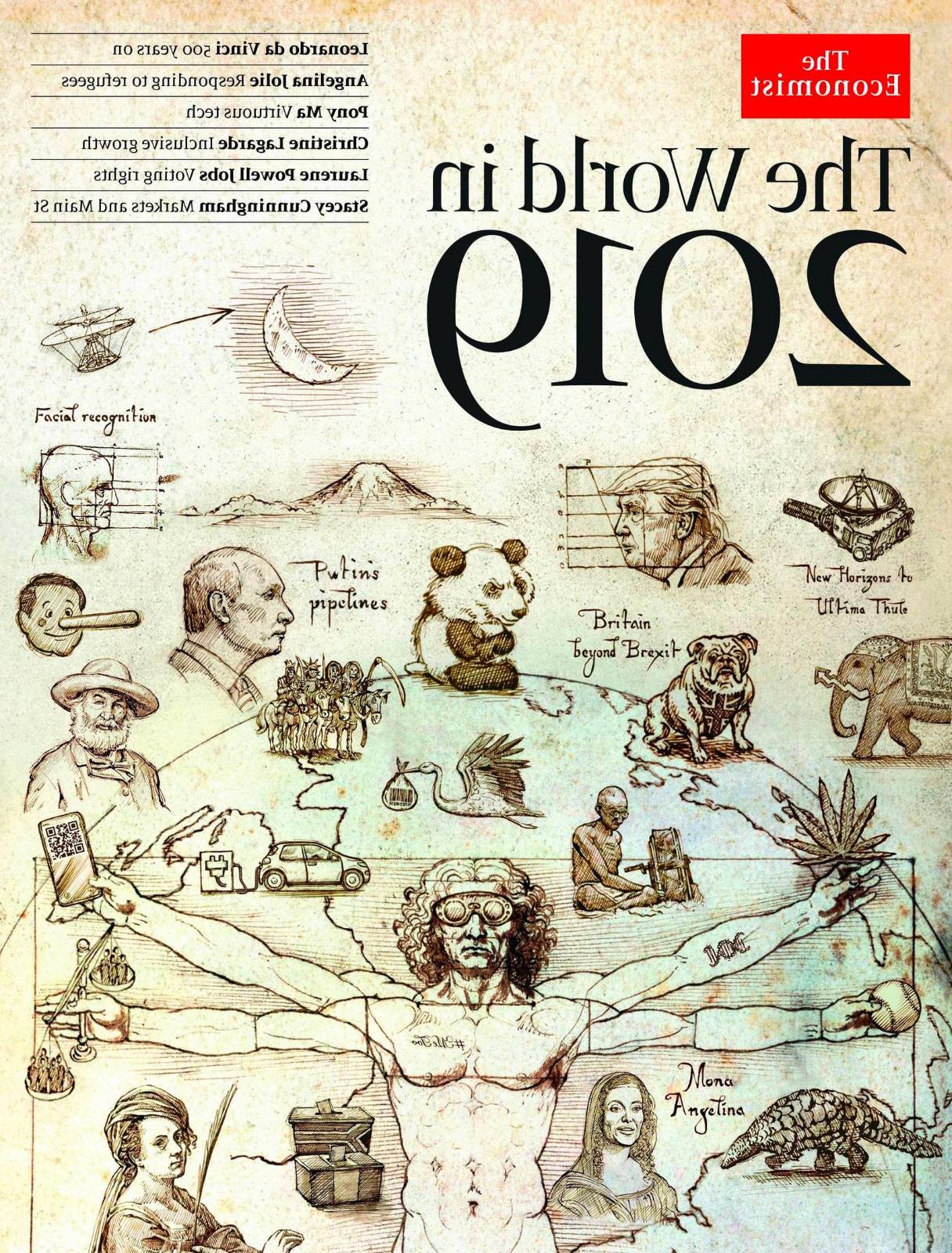
In case this is too difficult for you - some things to note: Four horsemen of the apacalypse, Statue of Liberty wearing a facemask, Vetruvian Man with QR code (Vaccine passport), DNA mark on his arm, wearing virtual reality glasses... The animal bottom right is a Pangolin. Scales of Justice are well tipped/skewed, facial recognition, electric cars, Putin's pipelines, China and Brexit feature highly along with the lieing media (Pinnochio) and #metoo. I smell Predictive Programming.
- More insights in the explainer here (backup copy here) - including why it is backwards...
That's it!
No one can be told what The Matrix is.**\ You have to see it for yourself.
Do share this newsletter with any of your friends and family who might be interested.
You can also email me at: LetterFrom@rogerprice.me
💡Enjoy the newsletters in your own language : Dutch, French, German, Serbian, Chinese Traditional & Simplified, Thai and Burmese.
-
-
 @ 57d1a264:69f1fee1
2025-05-13 06:32:15
@ 57d1a264:69f1fee1
2025-05-13 06:32:15You don’t have to be a type designer to appreciate what goes into the design of a letterform. In fact, even if you’re just a humble graphic designer, you should have a basic knowledge of what constructs the type you employ.
Typography, for all its concepts, expectations, implications, connotations and artistry, is, ultimately, a system. Just like a body has bones and muscles, every letterform has parts that give it shape, rhythm, and character.
If you're a creative working with type, learning the names of these parts helps you communicate clearly, better analyze your work and others, and design with precision. Everything comes down to a foundational understanding of the anatomy of the letterform and its essential component. So let’s help you with that.
Pangram Pangram Foundry is where the art of typography meets unparalleled craftsmanship. Established in 2018 by designer Mat Desjardins, Pangram Pangram has swiftly risen to become a globally recognized independent type foundry, admired and trusted by industry peers and the design community alike.
Read more about the anatomy of fonts at https://pangrampangram.com/blogs/journal/anatomy-of-the-letterform
originally posted at https://stacker.news/items/978828
-
 @ 0fa80bd3:ea7325de
2025-04-09 21:19:39
@ 0fa80bd3:ea7325de
2025-04-09 21:19:39DAOs promised decentralization. They offered a system where every member could influence a project's direction, where money and power were transparently distributed, and decisions were made through voting. All of it recorded immutably on the blockchain, free from middlemen.
But something didn’t work out. In practice, most DAOs haven’t evolved into living, self-organizing organisms. They became something else: clubs where participation is unevenly distributed. Leaders remained - only now without formal titles. They hold influence through control over communications, task framing, and community dynamics. Centralization still exists, just wrapped in a new package.
But there's a second, less obvious problem. Crowds can’t create strategy. In DAOs, people vote for what "feels right to the majority." But strategy isn’t about what feels good - it’s about what’s necessary. Difficult, unpopular, yet forward-looking decisions often fail when put to a vote. A founder’s vision is a risk. But in healthy teams, it’s that risk that drives progress. In DAOs, risk is almost always diluted until it becomes something safe and vague.
Instead of empowering leaders, DAOs often neutralize them. This is why many DAOs resemble consensus machines. Everyone talks, debates, and participates, but very little actually gets done. One person says, “Let’s jump,” and five others respond, “Let’s discuss that first.” This dynamic might work for open forums, but not for action.
Decentralization works when there’s trust and delegation, not just voting. Until DAOs develop effective systems for assigning roles, taking ownership, and acting with flexibility, they will keep losing ground to old-fashioned startups led by charismatic founders with a clear vision.
We’ve seen this in many real-world cases. Take MakerDAO, one of the most mature and technically sophisticated DAOs. Its governance token (MKR) holders vote on everything from interest rates to protocol upgrades. While this has allowed for transparency and community involvement, the process is often slow and bureaucratic. Complex proposals stall. Strategic pivots become hard to implement. And in 2023, a controversial proposal to allocate billions to real-world assets passed only narrowly, after months of infighting - highlighting how vision and execution can get stuck in the mud of distributed governance.
On the other hand, Uniswap DAO, responsible for the largest decentralized exchange, raised governance participation only after launching a delegation system where token holders could choose trusted representatives. Still, much of the activity is limited to a small group of active contributors. The vast majority of token holders remain passive. This raises the question: is it really community-led, or just a formalized power structure with lower transparency?
Then there’s ConstitutionDAO, an experiment that went viral. It raised over $40 million in days to try and buy a copy of the U.S. Constitution. But despite the hype, the DAO failed to win the auction. Afterwards, it struggled with refund logistics, communication breakdowns, and confusion over governance. It was a perfect example of collective enthusiasm without infrastructure or planning - proof that a DAO can raise capital fast but still lack cohesion.
Not all efforts have failed. Projects like Gitcoin DAO have made progress by incentivizing small, individual contributions. Their quadratic funding mechanism rewards projects based on the number of contributors, not just the size of donations, helping to elevate grassroots initiatives. But even here, long-term strategy often falls back on a core group of organizers rather than broad community consensus.
The pattern is clear: when the stakes are low or the tasks are modular, DAOs can coordinate well. But when bold moves are needed—when someone has to take responsibility and act under uncertainty DAOs often freeze. In the name of consensus, they lose momentum.
That’s why the organization of the future can’t rely purely on decentralization. It must encourage individual initiative and the ability to take calculated risks. People need to see their contribution not just as a vote, but as a role with clear actions and expected outcomes. When the situation demands, they should be empowered to act first and present the results to the community afterwards allowing for both autonomy and accountability. That’s not a flaw in the system. It’s how real progress happens.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28There's a problem with using Git concepts for everything
We've been seeing a surge in applications that use Git to store other things than code, or that are based on Git concepts and so enable "forking, merging and distributed collaboration" for things like blogs, recipes, literature, music composition, normal files in a filesystem, databases.
The problem with all this is they will either:
- assume the user will commit manually and expect that commit to be composed by a set of meaningful changes, and the commiter will also add a message to the commit, describing that set of meaningful, related changes; or
- try to make the committing process automatic and hide it from the user, so will producing meaningless commits, based on random changes in many different files (it's not "files" if we are talking about a recipe or rows in a table, but let's say "files" for the sake of clarity) that will probably not be related and not reduceable to a meaningful commit message, or maybe the commit will contain only the changes to a single file, and its commit message would be equivalent to "updated
<name of the file>".
Programmers, when using Git, think in Git, i.e., they work with version control in their minds. They try hard to commit together only sets of meaningful and related changes, even when they happen to make unrelated changes in the meantime, and that's why there are commands like
git add -pand many others.Normal people, to whom many of these git-based tools are intended to (and even programmers when out of their code-world), are much less prone to think in Git, and that's why another kind of abstraction for fork-merge-collaborate in non-code environments must be used.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Custom spreadsheets
The idea was to use it to make an app that would serve as custom database for everything and interact with the spreadsheet so people could play and calculate with their values after they were created by the custom app, something like an MS Access integrated with Excel?
My first attempt that worked (I believe there was an attempt before but I have probably deleted it from everywhere) was this
react-microspreadsheetthing (at the time calledreact-spreadsheetbefore I donated the npm name to someone who asked):This was a very good spreadsheet component that did many things current "react spreadsheet" components out there don't do. It had formulas; support for that handle thing that you pulled with the mouse and it autofilled cells with a pattern; it had keyboard navigation with Ctrl, Shift, Ctrl+Shift; it had that thing through which you copy-pasted formulas and they would change their parameters depending on where you pasted them (implemented in a very poor manner because I was using and thinking about Excel in baby mode at the time).
Then I tried to make it into "a small sheet you can share" kind of app through assemblymade.com, and eventually as I tried to add more things bugs began to appear.
Then there was
cycle6-spreadsheet:If I remember well this was very similar to the other one, although made almost 2 years after. Despite having the same initial goal of the other (the multi-app custom database thing) it only yielded:
- Sidesheet, a Chrome extension that opened a spreadsheet on the side of the screen that you could use to make calculations and so on. It worked, but had too many bugs that probably caused me to give up entirely.
I'm not sure which of the two spreadsheets above powers http://sheets.alhur.es.
-
 @ aa8de34f:a6ffe696
2025-03-31 21:48:50
@ aa8de34f:a6ffe696
2025-03-31 21:48:50In seinem Beitrag vom 30. März 2025 fragt Henning Rosenbusch auf Telegram angesichts zunehmender digitaler Kontrolle und staatlicher Allmacht:
„Wie soll sich gegen eine solche Tyrannei noch ein Widerstand formieren können, selbst im Untergrund? Sehe ich nicht.“\ (Quelle: t.me/rosenbusch/25228)
Er beschreibt damit ein Gefühl der Ohnmacht, das viele teilen: Eine Welt, in der Totalitarismus nicht mehr mit Panzern, sondern mit Algorithmen kommt. Wo Zugriff auf Geld, Meinungsfreiheit und Teilhabe vom Wohlverhalten abhängt. Der Bürger als kontrollierbare Variable im Code des Staates.\ Die Frage ist berechtigt. Doch die Antwort darauf liegt nicht in alten Widerstandsbildern – sondern in einer neuen Realität.
-- Denn es braucht keinen Untergrund mehr. --
Der Widerstand der Zukunft trägt keinen Tarnanzug. Er ist nicht konspirativ, sondern transparent. Nicht bewaffnet, sondern mathematisch beweisbar. Bitcoin steht nicht am Rand dieser Entwicklung – es ist ihr Fundament. Eine Bastion aus physikalischer Realität, spieltheoretischem Schutz und ökonomischer Wahrheit. Es ist nicht unfehlbar, aber unbestechlich. Nicht perfekt, aber immun gegen zentrale Willkür.
Hier entsteht kein „digitales Gegenreich“, sondern eine dezentrale Renaissance. Keine Revolte aus Wut, sondern eine stille Abkehr: von Zwang zu Freiwilligkeit, von Abhängigkeit zu Selbstverantwortung. Diese Revolution führt keine Kriege. Sie braucht keine Führer. Sie ist ein Netzwerk. Jeder Knoten ein Individuum. Jede Entscheidung ein Akt der Selbstermächtigung.
Weltweit wachsen Freiheits-Zitadellen aus dieser Idee: wirtschaftlich autark, digital souverän, lokal verankert und global vernetzt. Sie sind keine Utopien im luftleeren Raum, sondern konkrete Realitäten – angetrieben von Energie, Code und dem menschlichen Wunsch nach Würde.
Der Globalismus alter Prägung – zentralistisch, monopolistisch, bevormundend – wird an seiner eigenen Hybris zerbrechen. Seine Werkzeuge der Kontrolle werden ihn nicht retten. Im Gegenteil: Seine Geister werden ihn verfolgen und erlegen.
Und während die alten Mächte um Erhalt kämpfen, wächst eine neue Welt – nicht im Schatten, sondern im Offenen. Nicht auf Gewalt gebaut, sondern auf Mathematik, Physik und Freiheit.
Die Tyrannei sieht keinen Widerstand.\ Weil sie nicht erkennt, dass er längst begonnen hat.\ Unwiderruflich. Leise. Überall.
-
 @ 57d1a264:69f1fee1
2025-05-13 06:21:36
@ 57d1a264:69f1fee1
2025-05-13 06:21:36Steve Jobs sent me an email saying “Great idea, thank you."
Wait, what? What was the great idea?
new guy at NeXT In October of 1991, I was a new Systems Engineer at NeXT. NeXT, of course, was the company Steve Jobs had founded after leaving Apple in 1985, and which eventually merged back into Apple in 1996. I was one of three employees in Canada, and I think NeXT had about 400 people total.
NeXTMail Mail on the NeXT Computer was pretty amazing in 1991. Multimedia! Fonts! Attachments! Sounds! It’s hard to overstate how cool that was compared to the command line email everybody was used to. Every NeXT user got this email from Steve when they started up their computer.
That message included an attachment of what NeXT called Lip Service, the crazy idea that you could embed an audio file inside an email message. Crazy.
i have an idea
NeXT automatically set everybody up with a first-initial last-name address in the usual way, so I was shayman@next.com, and the big guy was sjobs@next.com.
A few colleagues had somehow acquired cooler email aliases - single letter things, or their first name, or a nickname or an easier to spell version, or whatever. Turns out NeXT had set up some sort of form where you could request an email alias that would redirect to whatever your real email address was.
I also noticed that even though there were seven or eight people at NeXT named Steve, nobody was using the email alias steve@next.com.
So late one Friday night, two weeks into the job, I figured, naively, what the heck, nobody else seems to want it, so I filled in the form asking for steve@next.com to be forwarded to me, shayman@next.com.
In the back of my mind was a vague idea that maybe somebody would have to approve this. But no, it all got set up automatically, and …
Continue reading at https://blog.hayman.net/2025/05/06/from-steve-jobs-great-idea.html
originally posted at https://stacker.news/items/978825
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28P2P reputation thing
Each node shares a blob of the reputations they have, which includes a confidence number. The number comes from the fact that reputations are inherited from other nodes they trust and averaged by their confidence in these. Everything is mixed for plausible deniability. By default a node only shares their stuff with people they manually add, to prevent government from crawling everybody's database. Also to each added friend nodes share a different identity/pubkey (like giving a new Bitcoin address for every transaction) (derived from hip32) (and since each identity can only be contacted by one other entity the node filters incoming connections to download their database: "this identity already been used? no, yes, used with which peer?").
Network protocol
Maybe the data uploader/offerer initiates connection to the receiver over Tor so there's only a Tor address for incoming data, never an address for a data source, i.e. everybody has an address, but only for requesting data.
How to request? Post an encrypted message in an IRC room or something similar (better if messages are stored for a while) targeted to the node/identity you want to download from, along with your Tor address. Once the node sees that it checks if you can download and contacts you.
The encrypted messages could have the target identity pubkey prefix such that the receiving node could try to decrypt only some if those with some probability of success.
Nodes can choose to share with anyone, share only with pre-approved people, share only with people who know one of their addresses/entities (works like a PIN, you give the address to someone in the street, that person can reach you, to the next person you give another address etc., you can even have a public address and share limited data with that).
Data model
Each entry in a database should be in the following format:
internal_id : real_world_identifier [, real_world_identifier...] : tagWhich means you can either associate one or multiple real world identifier with an internal id and associate the real person designated by these identifiers with a tag. the tag should be part of the standard or maybe negotiated between peers. it can be things like
scammer,thief,tax collectoretc., orhonest,good dentistetc. defining good enough labels may be tricky.internal_idshould be created by the user who made the record about the person.At first this is not necessary, but additional bloat can be added to the protocol if the federated automated message posting boards are working in the sense that each user can ask for more information about a given id and the author of that record can contact the person asking for information and deliver free text to them with the given information. For this to work the internal id must be a public key and the information delivered must be signed with the correspondent private key, so the receiver of the information will know it's not just some spammer inventing stuff, but actually the person who originated that record.
-
 @ d360efec:14907b5f
2025-05-13 00:39:56
@ d360efec:14907b5f
2025-05-13 00:39:56🚀📉 #BTC วิเคราะห์ H2! พุ่งชน 105K แล้วเจอแรงขาย... จับตา FVG 100.5K เป็นจุดวัดใจ! 👀📊
จากากรวิเคราะห์ทางเทคนิคสำหรับ #Bitcoin ในกรอบเวลา H2:
สัปดาห์ที่แล้ว #BTC ได้เบรคและพุ่งขึ้นอย่างแข็งแกร่งค่ะ 📈⚡ แต่เมื่อวันจันทร์ที่ผ่านมา ราคาได้ขึ้นไปชนแนวต้านบริเวณ 105,000 ดอลลาร์ แล้วเจอแรงขายย่อตัวลงมาตลอดทั้งวันค่ะ 🧱📉
ตอนนี้ ระดับที่น่าจับตาอย่างยิ่งคือโซน H4 FVG (Fair Value Gap ในกราฟ 4 ชั่วโมง) ที่ 100,500 ดอลลาร์ ค่ะ 🎯 (FVG คือโซนที่ราคาวิ่งผ่านไปเร็วๆ และมักเป็นบริเวณที่ราคามีโอกาสกลับมาทดสอบ/เติมเต็ม)
👇 โซน FVG ที่ 100.5K นี้ ยังคงเป็น Area of Interest ที่น่าสนใจสำหรับมองหาจังหวะ Long เพื่อลุ้นการขึ้นในคลื่นลูกถัดไปค่ะ!
🤔💡 อย่างไรก็ตาม การตัดสินใจเข้า Long หรือเทรดที่บริเวณนี้ ขึ้นอยู่กับว่าราคา แสดงปฏิกิริยาอย่างไรเมื่อมาถึงโซน 100.5K นี้ เพื่อยืนยันสัญญาณสำหรับการเคลื่อนไหวที่จะขึ้นสูงกว่าเดิมค่ะ!
เฝ้าดู Price Action ที่ระดับนี้อย่างใกล้ชิดนะคะ! 📍
BTC #Bitcoin #Crypto #คริปโต #TechnicalAnalysis #Trading #FVG #FairValueGap #PriceAction #MarketAnalysis #ลงทุนคริปโต #วิเคราะห์กราฟ #TradeSetup #ข่าวคริปโต #ตลาดคริปโต


-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28gravity
IPFS is nice as a personal archiving tool (edit: it's not). You store a bunch of data and make it available to the public.
The problem is that no one will ever know you have that data, therefore you need a place to publish it somewhere. Gravity was an attempt of being the tool for this job.
It was a website that showcased the collections from users, and it was also a command-line client that used your IPFS keys for authentication and allowed you to paste IPFS URIs and names and descriptions.
The site was intended to be easy to run so you could have multiple stellar bodies aggregating content and interact with them all in a standardized manner.
It also had an ActivityPub/"fediverse" integration so people could follow Gravity server users from Mastodon and friends and see new data they published as "tweets".
See also
-
 @ 0c469779:4b21d8b0
2025-03-11 10:52:49
@ 0c469779:4b21d8b0
2025-03-11 10:52:49Sobre el amor
Mi percepción del amor cambió con el tiempo. Leer literatura rusa, principalmente a Dostoevsky, te cambia la perspectiva sobre el amor y la vida en general.
Por mucho tiempo mi visión sobre la vida es que la misma se basa en el sufrimiento: también la Biblia dice esto. El amor es igual, en el amor se sufre y se banca a la otra persona. El problema es que hay una distinción de sufrimientos que por mucho tiempo no tuve en cuenta. Está el sufrimiento del sacrificio y el sufrimiento masoquista. Para mí eran indistintos.
Para mí el ideal era Aliosha y Natasha de Humillados y Ofendidos: estar con alguien que me amase tanto como Natasha a Aliosha, un amor inclusive autodestructivo para Natasha, pero real. Tiene algo de épico, inalcanzable. Un sufrimiento extremo, redentor, es una vara altísima que en la vida cotidiana no se manifiesta. O el amor de Sonia a Raskolnikov, quien se fue hasta Siberia mientras estuvo en prisión para que no se quede solo en Crimen y Castigo.
Este es el tipo de amor que yo esperaba. Y como no me pasó nada tan extremo y las situaciones que llegan a ocurrir en mi vida están lejos de ser tan extremas, me parecía hasta poco lo que estaba pidiendo y que nadie pueda quedarse conmigo me parecía insuficiente.
Ahora pienso que el amor no tiene por qué ser así. Es un pensamiento nuevo que todavía estoy construyendo, y me di cuenta cuando fui a la iglesia, a pesar de que no soy cristiano. La filosofía cristiana me gusta. Va conmigo. Tiene un enfoque de humildad, superación y comunidad que me recuerda al estoicismo.
El amor se trata de resaltar lo mejor que hay en el otro. Se trata de ser un plus, de ayudar. Por eso si uno no está en su mejor etapa, si no se está cómodo con uno mismo, no se puede amar de verdad. El amor empieza en uno mismo.
Los libros son un espejo, no necesariamente vas a aprender de ellos, sino que te muestran quién sos. Resaltás lo que te importa. Por eso a pesar de saber los tipos de amores que hay en los trabajos de Dostoevsky, cometí los mismos errores varias veces.
Ser mejor depende de uno mismo y cada día se pone el granito de arena.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28TiddlyWiki remoteStorage
TiddlyWiki is very good and useful, but since at this time I used multiple computers during the week, it wouldn't work for me to use it as a single file on my computer, so I had to hack its internal tiddler saving mechanism to instead save the raw data of each tiddler to remoteStorage and load them from that place also (ok, there was in theory a plugin system, but I had to read and understand the entire unformatted core source-code anyway).
There was also a server that fetched tiddlywikis from anyone's remoteStorage buckets (after authorization) and served these to the world, a quick and nice way to publish a TiddlyWiki -- which is a problem all people in TiddlyWiki struggle against.
See also
-
 @ 4857600b:30b502f4
2025-03-11 01:58:19
@ 4857600b:30b502f4
2025-03-11 01:58:19Key Findings
- Researchers at the University of Cambridge discovered that aspirin can help slow the spread of certain cancers, including breast, bowel, and prostate cancers
- The study was published in the journal Nature
How Aspirin Works Against Cancer
- Aspirin blocks thromboxane A2 (TXA2), a chemical produced by blood platelets
- TXA2 normally weakens T cells, which are crucial for fighting cancer
- By inhibiting TXA2, aspirin "unleashes" T cells to more effectively target and destroy cancer cells
Supporting Evidence
- Previous studies showed regular aspirin use was linked to:
- 31% reduction in cancer-specific mortality in breast cancer patients
- 9% decrease in recurrence/metastasis risk
- 25% reduction in colon cancer risk
Potential Impact
- Aspirin could be particularly effective in early stages of cancer
- It may help prevent metastasis, which causes 90% of cancer fatalities
- As an inexpensive treatment, it could be more accessible globally than antibody-based therapies
Cautions
- Experts warn against self-medicating with aspirin
- Potential risks include internal bleeding and stomach ulcers
- Patients should consult doctors before starting aspirin therapy
Next Steps
- Large-scale clinical trials to determine which cancer types and patients would benefit most
- Development of new drugs that mimic aspirin's benefits without side effects
Citations: Natural News
-
 @ eabee230:17fc7576
2025-05-12 14:38:11
@ eabee230:17fc7576
2025-05-12 14:38:11⚖️ຢ່າລືມສິ່ງທີ່ເຄີຍເກີດຂຶ້ນ ຮອດຊ່ວງທີ່ມີການປ່ຽນແປງລະບົບການເງິນຈາກລະບົບເງິນເກົ່າ ສູ່ລະບົບເງິນໃໝ່ມັນເຮັດໃຫ້ຄົນທີ່ລວຍກາຍເປັນຄົນທຸກໄດ້ເລີຍ ນ້ຳພັກນ້ຳແຮງທີ່ສະສົມມາດ້ວຍຄວາມເມື່ອຍແຕ່ບໍ່ສາມາດແລກເປັນເງິນລະບົບໃໝ່ໄດ້ທັງໝົດ ຖືກຈຳກັດຈຳນວນທີ່ກົດໝາຍວາງອອກມາໃຫ້ແລກ ເງິນທີ່ເຫຼືອນັ້ນປຽບຄືດັ່ງເສດເຈ້ຍ ເພາະມັນບໍ່ມີຢູ່ໃສຮັບອີກຕໍ່ໄປເພາະກົດໝາຍຈະນຳໃຊ້ສະກຸນໃໝ່ ປະຫວັດສາດເຮົາມີໃຫ້ເຫັນວ່າ ແລະ ເຄີຍຜ່ານມາແລ້ວຢ່າໃຫ້ຄົນລຸ້ນເຮົາຊຳ້ຮອຍເກົ່າ.
🕰️ຄົນທີ່ມີຄວາມຮູ້ ຫຼື ໃກ້ຊິດກັບແຫຼ່ງຂໍ້ມູນຂ່າວສານກໍຈະປ່ຽນເງິນທີ່ມີຢູ່ເປັນສິນສັບບໍ່ວ່າຈະເປັນທີ່ດິນ ແລະ ທອງຄຳທີ່ສາມາດຮັກສາມູນລະຄ່າໄດ້ເຮັດໃຫ້ເຂົາຍັງຮັກສາຄວາມມັ້ງຄັ້ງໃນລະບົບໃໝ່ໄດ້.
🕰️ໃຜທີ່ຕ້ອງການຈະຍ້າຍປະເທດກໍ່ຈະໃຊ້ສິ່ງທີ່ເປັນຊື່ກາງໃນການແລກປ່ຽນເປັນທີ່ຍ້ອມຮັບຫຼາຍນັ້ນກໍຄືທອງຄຳ ປ່ຽນຈາກເງິນລະບົບເກົ່າເປັນທອງຄຳເພື່ອທີ່ສາມາດປ່ຽນທອງຄຳເປັນສະກຸນເງິນທ້ອງຖິ່ນຢູ່ປະເທດປາຍທາງໄດ້.
🕰️ຈາກຜູ້ດີເມື່ອກ່ອນກາຍເປັນຄົນທຳມະດາຍ້ອນສັບສິນທີ່ມີ ບໍ່ສາມາດສົ່ງຕໍ່ສູ່ລູກຫຼານໄດ້. ການເກັບອອມເປັນສິ່ງທີ່ດີ ແຕ່ຖ້າໃຫ້ດີຕ້ອງເກັບອອມໃຫ້ຖືກບ່ອນ ຄົນທີ່ຮູ້ທັນປ່ຽນເງິນທີ່ມີຈາກລະບົບເກົ່າໄປສູ່ທອງຄຳ ເພາະທອງຄຳມັນເປັນສາກົນ.
ໃຜທີ່ເຂົ້າໃຈ ແລະ ມອງການໄກກວ່າກໍ່ສາມາດຮັກສາສິນສັບສູ່ລູກຫຼານໄດ້ ເກັບເຈ້ຍໃນປະລິມານທີ່ພໍໃຊ້ຈ່າຍ ປ່ຽນເຈ້ຍໃຫ້ເປັນສິ່ງທີ່ຮັກສາມູນລະຄ່າໄດ້ແທ້ຈິງ.🕰️ເຮົາໂຊກດີທີ່ເຄີຍມີບົດຮຽນມາແລ້ວ ເກີດຂຶ້ນຈິງໃນປະເທດເຮົາບໍ່ໄດ້ຢາກໃຫ້ທັງໝົດແຕ່ຢາກໃຫ້ສຶກສາ ແລະ ຕັ້ງຄຳຖາມວ່າທີ່ຜ່ານມາມັນເປັນແບບນີ້ແທ້ບໍ່ ເງິນທີ່ລັດຄວາມຄຸມ ເງິນປະລິມານບໍ່ຈຳກັດ ການໃຊ້ກົດໝາຍແບບບັງຄັບ. ຖ້າຄອບຄົວຫຼືຄົນໃກ້ໂຕທີ່ຍູ່ໃນຊ່ວງເຫດການນັ້ນແຕ່ຕັດສິນໃຈຜິດພາດທີ່ບໍ່ປ່ຽນເຈ້ຍເປັນສິນສັບ. ນີ້ແມ່ນໂອກາດທີ່ຈະແກ້ໄຂຂໍ້ຜິດພາດນັ້ນໂດຍຫັນມາສຶກສາເງິນແທ້ຈິງແລ້ວແມ່ນຍັງກັນແທ້ ເວລາມີຄ່າສຶກສາບິດຄອຍ.

fiatcurrency #bitcoin #gold #history #paymentsolutions #laokip #laostr
-
 @ b83a28b7:35919450
2025-05-16 19:13:43
@ b83a28b7:35919450
2025-05-16 19:13:43This is the body
-
 @ 57d1a264:69f1fee1
2025-05-11 06:23:03
@ 57d1a264:69f1fee1
2025-05-11 06:23:03Past week summary
From a Self Custody for Organizations perspective, after analyzing the existing protocols (Cerberus, 10xSecurityBTCguide and Glacier) and reading a bunch of relates articles and guides, have wrapped to the conclusion that this format it is good to have as reference. However, something else is needed. For example, a summary or a map of the whole process to provide an overview, plus a way to deliver all the information and the multy-process in a more enjoyable way. Not a job for this hackathon, but with the right collaborations I assume it's possible to: - build something that might introduce a bit more quests and gamification - provide a learning environment (with testnet funds) could also be crucial on educating those unfamiliar with bitcoin onchain dynamics.
Have been learning more and playing around practicing best accessibility practices and how it could be applied to a desktop software like Bitcoin Safe. Thanks to @johnjherzog for providing a screen recording of his first experience and @jasonb for suggesting the tools to be used. (in this case tested/testing on Windows with the Accessibility Insights app). Some insight shared have been also applied to the website, running a full accessibility check (under WCAG 2.2 ADA, and Section 508 standards) with 4 different plugins and two online tools. I recognize that not all of them works and analyze the same parameters, indeed they complement each other providing a more accurate review.
For Bitcoin Safe interface improvements, many suggestions have been shared with @andreasgriffin , including: - a new iconset, including a micro-set to display the number of confirmed blocs for each transaction - a redesigned History/Dashboard - small refinements like adding missing columns on the tables - allow the user to select which columns to be displayed - sorting of unconfirmed transactions - Defining a new style for design elements like mempool blocks and quick receive boxes You can find below some screenshots with my proposals that hopefully will be included in the next release.
Last achievement this week was to prepare the website https://Safe.BTC.pub, the container where all the outcomes f this experiment will be published. You can have a look, just consider it still WIP. Branding for the project has also been finalized and available in this penpot file https://design.penpot.app/#/workspace?team-id=cec80257-5021-8137-8005-eab60c043dd6&project-id=cec80257-5021-8137-8005-eab60c043dd8&file-id=95aea877-d515-80ac-8006-23a251886db3&page-id=132f519a-39f4-80db-8006-2a41c364a545
What's for next week
After spending most of the time learning and reading material, this coming week will be focused on deliverables. The goal as planned will be to provide: - Finalized Safe₿its brand and improve overall desktop app experience, including categorization of transactions and addresses - An accessibility report or guide for Bitcoin Safe and support to implement best practices - A first draft of the Self-Custody for Organizations guide/framework/protocol, ideally delivered through the website http://Safe.BTC.pub in written format, but also as FlowChart to help have an overview of the whole resources needed and the process itself. This will clearly define preparations and tools/hardwares needed to successfully complete the process.
To learn more about the project, you can visit: Designathon website: https://event.bitcoin.design/#project-recj4SVNLLkuWHpKq Discord channel: https://discord.com/channels/903125802726596648/1369200271632236574 Previous SN posts: https://stacker.news/items/974489/r/DeSign_r and https://stacker.news/items/974488/r/DeSign_r
Stay tuned, more will be happening this coming week
originally posted at https://stacker.news/items/977190
-
 @ 3a9a4c49:f774dd7a
2025-05-16 18:05:58
@ 3a9a4c49:f774dd7a
2025-05-16 18:05:58Keeping a home safe and functioning means being sure that your boiler is functioning well and having a valid Gas Safety Certificate. If you're looking for 'https://certificates4uk.co.uk/boiler-replacement-services/' or a trusted Gas Safety Certificate company near me, stop searching at Certificates 4 UK. Our services include professional boiler servicing, repair, and safety certification to keep your home compliant and safe.
**Why Certificates 4 UK for Boiler Repairs?
** A malfunctioning boiler means high energy bills, cold showers, and, ultimately, gas leaks that might be harmful. Hence, timely boiler service near me is of prime importance. At Certificates 4 UK, our Gas Safe registered engineers can promptly and accurately troubleshoot and carry out any repairs on your boiler. Whether it is a faulty thermostat, low pressure, or a complete breakdown, we restore your heating to peak performance.
****Common Boiler Problems We Fix:
- No heating or hot water is often caused by broken diaphragms, airlocks, or valve failures.
- Leaking or dripping boilers could be due to broken internal components or high pressure.
- Strange noises(banging, gurgling, whistling) usually indicate limescale buildup or trapped air.
- The pilot light keeps going out this may indicate a faulty thermocouple or draught affecting the flame.
- Boiler pressure issues: Besides improvement of efficiency, the pressure should not be excessively high or low in any boiler.
Our experts offer same-day emergency repair services to make sure you never have to cope without the heating when needed.
**
Significance of Gas Safety Certificate.
** Gas Safety Certification, or CP12, is a necessary proviso for landlords. Homeowners also are supposed to do annual gas safety checks to avail against carbon monoxide leakages and gas-based catastrophes. When looking for an honest https://certificates4uk.co.uk/gas-services/, Certificates 4 UK should be a prime consideration to provide you with quick, cheap, and legally satisfactory inspections.
**What is a part of the Gas Safety Check?
**
## **Our Gas Safe engineers will:
** * Inspect all gas appliances (boilers, cookers, and fires) to detect leaks or defects. * Check ventilation and flue systems to ensure no obstruction of exhaust flow. * Test gas pressure and safety controls. * Submit a report and provide a Gas Safety Certificate if all equipment passes.
Every landlord is expected to renew this certificate once a year and provide a copy to their tenants. Otherwise, there are hefty-to-hidden fines, ' fines or imprisonment.'
**Why Trust Certificates 4 UK?
** * Gas Safe Registered Engineers : All our technicians are fully qualified and approved. * Fast & Reliable Service : Same-day and next-day appointments. * Competitive Pricing : Reasonable rates without having to cut costs on quality. * Nationwide Coverage Helping homeowners and landlords throughout the UK.
**Book Your Boiler Repair or Gas Safety Check Today!
** Do not wait for a day when your boiler gives up on you or when your gas certificate lapses! Call Certificates 4 UK today for professional boiler repair near me or a Gas Safety Certificate inspection. By going with Certificates 4 UK, you are assured of high-quality boiler repair and gas safety compliance. Whenever you need an emergency fix or an annual inspection, we have got you covered. Lastly, put any doubts about 'boiler repairs near me' or 'gas safety certificate companies near me' to rest; rest assured, the experts at Certificates 4 UK will provide you with peace of mind!
-
 @ 57d1a264:69f1fee1
2025-05-11 05:52:56
@ 57d1a264:69f1fee1
2025-05-11 05:52:56Past week summary
From a Self Custody for Organizations perspective, after analyzing the existing protocols (Cerberus, 10xSecurityBTCguide and Glacier) and reading a bunch of relates articles and guides, have wrapped to the conclusion that this format it is good to have as reference. However, something else is needed. For example, a summary or a map of the whole process to provide an overview, plus a way to deliver all the information and the multy-process in a more enjoyable way. Not a job for this hackathon, but with the right collaborations I assume it's possible to: - build something that might introduce a bit more quests and gamification - provide a learning environment (with testnet funds) could also be crucial on educating those unfamiliar with bitcoin onchain dynamics.
Have been learning more and playing around practicing best accessibility practices and how it could be applied to a desktop software like Bitcoin Safe. Thanks to @johnjherzog for providing a screen recording of his first experience and @jasonbohio for suggesting the tools to be used. (in this case tested/testing on Windows with the Accessibility Insights app). Some insight shared have been also applied to the website, running a full accessibility check (under WCAG 2.2 ADA, and Section 508 standards) with 4 different plugins and two online tools. I recognize that not all of them works and analyze the same parameters, indeed they complement each other providing a more accurate review.
For Bitcoin Safe interface improvements, many suggestions have been shared with @andreasgriffin , including: - a new iconset, including a micro-set to display the number of confirmed blocs for each transaction - a redesigned History/Dashboard - small refinements like adding missing columns on the tables - allow the user to select which columns to be displayed - sorting of unconfirmed transactions - Defining a new style for design elements like mempool blocks and quick receive boxes You can find below some screenshots with my proposals that hopefully will be included in the next release.
Last achievement this week was to prepare the website https://Safe.BTC.pub, the container where all the outcomes f this experiment will be published. You can have a look, just consider it still WIP. Branding for the project has also been finalized and available in this penpot file https://design.penpot.app/#/workspace?team-id=cec80257-5021-8137-8005-eab60c043dd6&project-id=cec80257-5021-8137-8005-eab60c043dd8&file-id=95aea877-d515-80ac-8006-23a251886db3&page-id=132f519a-39f4-80db-8006-2a41c364a545
What's for next week
After spending most of the time learning and reading material, this coming week will be focused on deliverables. The goal as planned will be to provide: - Finalized Safe₿its brand and improve overall desktop app experience, including categorization of transactions and addresses - An accessibility report or guide for Bitcoin Safe and support to implement best practices - A first draft of the Self-Custody for Organizations guide/framework/protocol, ideally delivered through the website http://Safe.BTC.pub in written format, but also as FlowChart to help have an overview of the whole resources needed and the process itself. This will clearly define preparations and tools/hardwares needed to successfully complete the process.
To learn more about the project, you can visit: Designathon website: https://event.bitcoin.design/#project-recj4SVNLLkuWHpKq Discord channel: https://discord.com/channels/903125802726596648/1369200271632236574 Previous SN posts: https://stacker.news/items/974489/r/DeSign_r and https://stacker.news/items/974488/r/DeSign_r
Stay tuned, more will be happening this coming week
originally posted at https://stacker.news/items/977180
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Democracia na América
Alexis de Tocqueville escreveu um livro só elogiando o sistema político dos Estados Unidos. E mesmo tendo sido assim, e mesmo tendo escrito o seu livro quase 100 anos antes do mais precoce sinal de decadência da democracia na América, percebeu coisas que até hoje quase ninguém percebe: o mandato da suprema corte é um enorme poder, uma força centralizadora, imune ao voto popular e com poderes altamente indefinidos e por isso mesmo ilimitados.
Não sei se ele concluiu, porém, que não existe nem pode existir balanço perfeito entre poderes. Sempre haverá furos.
De qualquer maneira, o homem é um gênio apenas por ter percebido isso e outras coisas, como o fato da figura do presidente, também obviamente um elemento centralizador, não ser tão poderosa quanto a figura de um rei da França, por exemplo. Mas ao mesmo tempo, por entre o véu de elogios (sempre muito sóbrios) deixou escapar que provavelmente também achava que não poderia durar para sempre a fraqueza do cargo de presidente.
-
 @ c9badfea:610f861a
2025-05-16 17:57:20
@ c9badfea:610f861a
2025-05-16 17:57:20- Install Lemuroid (it's free and open source)
- Launch the app, enable notifications, and select a directory for your games (e.g.
/Download/ROMs) - Download game ROMs and place them in the folder from the previous step (see links below)
- Open Lemuroid again, navigate to the Home tab, and tap the downloaded game
- Enjoy!
Some ROM Sources
ℹ️ An internet connection is only required when opening a game for the first time to download the emulator core per system (e.g. Gameboy or PS2)
ℹ️ Supported ROM file formats include
.nes,.gba,.sfc,.gb,.iso,.bin, and.zipℹ️ You may need to extract downloaded ROM files if they are packaged as archives (e.g.
.7z,.rar, or.zip) -
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28busca múltipla na estante virtual

A single-page app made in Elm with a Go backend that scrapped estantevirtual.com.br in real-time for search results of multiple different search terms and aggregated the results per book store, so when you want to buy many books you can find the stores that have the biggest part of what you want and buy everything together, paying less for the delivery fee.
It had a very weird unicode issue I never managed to solve, something with the encoding estantevirtual.com.br used.
I also planned to build the entire checkout flow directly in this UI, but then decided it wasn't worth it. The search flow only was already good enough.
-
 @ c631e267:c2b78d3e
2025-05-10 09:50:45
@ c631e267:c2b78d3e
2025-05-10 09:50:45Information ohne Reflexion ist geistiger Flugsand. \ Ernst Reinhardt
Der lateinische Ausdruck «Quo vadis» als Frage nach einer Entwicklung oder Ausrichtung hat biblische Wurzeln. Er wird aber auch in unserer Alltagssprache verwendet, laut Duden meist als Ausdruck von Besorgnis oder Skepsis im Sinne von: «Wohin wird das führen?»
Der Sinn und Zweck von so mancher politischen Entscheidung erschließt sich heutzutage nicht mehr so leicht, und viele Trends können uns Sorge bereiten. Das sind einerseits sehr konkrete Themen wie die zunehmende Militarisierung und die geschichtsvergessene Kriegstreiberei in Europa, deren Feindbildpflege aktuell beim Gedenken an das Ende des Zweiten Weltkriegs beschämende Formen annimmt.
Auch das hohe Gut der Schweizer Neutralität scheint immer mehr in Gefahr. Die schleichende Bewegung der Eidgenossenschaft in Richtung NATO und damit weg von einer Vermittlerposition erhält auch durch den neuen Verteidigungsminister Anschub. Martin Pfister möchte eine stärkere Einbindung in die europäische Verteidigungsarchitektur, verwechselt bei der Argumentation jedoch Ursache und Wirkung.
Das Thema Gesundheit ist als Zugpferd für Geschäfte und Kontrolle offenbar schon zuverlässig etabliert. Die hauptsächlich privat finanzierte Weltgesundheitsorganisation (WHO) ist dabei durch ein Netzwerk von sogenannten «Collaborating Centres» sogar so weit in nationale Einrichtungen eingedrungen, dass man sich fragen kann, ob diese nicht von Genf aus gesteuert werden.
Das Schweizer Bundesamt für Gesundheit (BAG) übernimmt in dieser Funktion ebenso von der WHO definierte Aufgaben und Pflichten wie das deutsche Robert Koch-Institut (RKI). Gegen die Covid-«Impfung» für Schwangere, die das BAG empfiehlt, obwohl es fehlende wissenschaftliche Belege für deren Schutzwirkung einräumt, formiert sich im Tessin gerade Widerstand.
Unter dem Stichwort «Gesundheitssicherheit» werden uns die Bestrebungen verkauft, essenzielle Dienste mit einer biometrischen digitalen ID zu verknüpfen. Das dient dem Profit mit unseren Daten und führt im Ergebnis zum Verlust unserer demokratischen Freiheiten. Die deutsche elektronische Patientenakte (ePA) ist ein Element mit solchem Potenzial. Die Schweizer Bürger haben gerade ein Referendum gegen das revidierte E-ID-Gesetz erzwungen. In Thailand ist seit Anfang Mai für die Einreise eine «Digital Arrival Card» notwendig, die mit ihrer Gesundheitserklärung einen Impfpass «durch die Hintertür» befürchten lässt.
Der massive Blackout auf der iberischen Halbinsel hat vermehrt Fragen dazu aufgeworfen, wohin uns Klimawandel-Hysterie und «grüne» Energiepolitik führen werden. Meine Kollegin Wiltrud Schwetje ist dem nachgegangen und hat in mehreren Beiträgen darüber berichtet. Wenig überraschend führen interessante Spuren mal wieder zu internationalen Großbanken, Globalisten und zur EU-Kommission.
Zunehmend bedenklich ist aber ganz allgemein auch die manifestierte Spaltung unserer Gesellschaften. Angesichts der tiefen und sorgsam gepflegten Gräben fällt es inzwischen schwer, eine zukunftsfähige Perspektive zu erkennen. Umso begrüßenswerter sind Initiativen wie die Kölner Veranstaltungsreihe «Neue Visionen für die Zukunft». Diese möchte die Diskussionskultur reanimieren und dazu beitragen, dass Menschen wieder ohne Angst und ergebnisoffen über kontroverse Themen der Zeit sprechen.
Quo vadis – Wohin gehen wir also? Die Suche nach Orientierung in diesem vermeintlichen Chaos führt auch zur Reflexion über den eigenen Lebensweg. Das ist positiv insofern, als wir daraus Kraft schöpfen können. Ob derweil der neue Papst, dessen «Vorgänger» Petrus unsere Ausgangsfrage durch die christliche Legende zugeschrieben wird, dabei eine Rolle spielt, muss jede/r selbst wissen. Mir persönlich ist allein schon ein Führungsanspruch wie der des Petrusprimats der römisch-katholischen Kirche eher suspekt.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 57d1a264:69f1fee1
2025-05-10 05:45:52
@ 57d1a264:69f1fee1
2025-05-10 05:45:52Finale: once the industry-standard of music notation software, now a cautionary tale. In this video, I explore how it slowly lost its crown through decades of missed opportunities - eventually leading to creative collapse due to various bureaucratic intrigues, unforeseen technological changes and some of the jankiest UI/UX you've ever seen.
https://www.youtube.com/watch?v=Yqaon6YHzaU
originally posted at https://stacker.news/items/976219
-
 @ 7e6f9018:a6bbbce5
2025-05-16 17:32:56
@ 7e6f9018:a6bbbce5
2025-05-16 17:32:56The rental population in Spain has grown from about 5 million in 2005 to around 10 million in 2025. During that same period, Spain's total population has increased by 6 million people, from 43 to 49 million. In other words, the entire population growth over the past 20 years has essentially gone straight into the rental market.
This demographic growth is not due to natural increase, Spain has one of the lowest fertility rates in the world. Instead, population growth is driven by a positive migratory balance, which has been the main factor behind the rise in rental demand.
This increased demand for rentals has pushed up rental prices, which have significantly outpaced the growth in property sale prices. That didn’t happen during the Great Financial Crisis. The growth in both demand and prices is allowing rental profitability to remain at the high end of the curve—around 5% net.
This situation explains the rise in housing squatting, from 2,000 cases in 2010 to 16,000 in 2024. Since the immigrant population is the main driver of this surge in rental demand, it is more vulnerable to squatting, as they often have no alternative housing when they are unable to pay.
The unemployment rate is currently low, however, if it were to rise (as it did during the Great Financial Crisis and other periods in the past), squatting would likely increase significantly, representing the main risk to the current real estate market in Spain.
-
 @ c9e9bdc0:e4dbe9b8
2025-05-16 17:00:09
@ c9e9bdc0:e4dbe9b8
2025-05-16 17:00:09Today we’re launching Buzzbot Express: a clean, targeted way to drive engagement and reward your audience with sats.
Here’s how it works:
-
Tag @buzzbot express [amount] (e.g.,
@buzzbot express 5000) -
Pay the invoice sent to your DMs
-
After 12 hours, one random liker and one random commenter each win **50% of the sats **(6% fee)
Since launching Buzzbot, we’ve seen a wide range of creative use cases. But the clearest path to long-term value may lie in branded content and decentralized promotion.
From plebs promoting value-for-value concerts to podcasters pushing new episodes, Buzzbot Express gives creators and brands a tool to generate real energy around a post.
Paying for engagement might feel off-brand to some, but if you’re promoting a product, a song, or an event, Buzzbot Express offers a clean, transparent way to generate real momentum.
The invention of Zaps opened the fifth dimension of social media. They are not just another feature added to the stack. They are an exponential amplifier that transforms attention into economic energy.
At Buzzbot, we believe this new creator economy can and should include advertisers.
The days of brands paying millions to ad firms, hiring Hollywood talent, and forcing campaigns into feeds are fading. That model made sense on centralized, algorithmic platforms, but it doesn’t belong on Nostr.
Instead, brands can spend that same money directly with creators who align with their values. Or better yet, they can reward audiences for engaging honestly.
That’s where Buzzbot comes in.
Buzzbot Express is a small step toward this future. Try it out — and let us know what you think.
Pay attention.
-
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28requesthub.xyz
An app that was supposed to be some kind of declarative connector between two services, one that sent webhooks and the other that accepted HTTP requests of any kind. You would proxy and transform the webhooks using RequestHub and create a new request to the other service using that data.
The transformations were declared in the almighty
jqlanguage.It worked and had other functions planned for the future, but I guess it was too arcane, even I was confused by it sometimes.
Also it was very prone to spam (involuntary) attacks like some that did happen. Maybe it would work better in a world of anonymous satoshi payments.
Later I tried to revive it as a Trello Power-Up that would create comments on cards automatically according to some transformation rules and webhooks received.
-
 @ 57d1a264:69f1fee1
2025-05-10 05:34:46
@ 57d1a264:69f1fee1
2025-05-10 05:34:46
For generations before generative text, writers have used the em dash to hop between thoughts, emotions, and ideas. Dickens shaped his morality tales with it, Woolf’s stream-of-consciousness flowed through it, Kerouac let it drive his jazz-like prose. Today, Sally Rooney threads it through her quiet truths of the heart.
But this beloved punctuation mark has become a casualty of the algorithmic age. The em dash has been so widely adopted by AI-generated text that even when used by human hands, it begs the question: was this actually written or apathetically prompted?
The battle for the soul of writing is in full swing. And the human fightback starts here. With a new punctuation mark that serves as a symbol of real pondering, genuine daydreaming, and true editorial wordsmithery. Inspired by Descartes’ belief that thinking makes us human, the am dash is a small but powerful testament that the words you’ve painstakingly and poetically pulled together are unequivocally, certifiably, and delightfully your own.
Let's reclain writig from AI—oneam dash at time.
Download the fonts:
— Aereal https://bit.ly/3EO6fo8 — Times New Human https://bit.ly/4jQTcRS
Learn more about the am dash
https://www.theamdash.com
originally posted at https://stacker.news/items/976218
-
 @ 05a0f81e:fc032124
2025-05-16 16:51:11
@ 05a0f81e:fc032124
2025-05-16 16:51:11In the year 2023, a man known as RTD. HAMZA AL-MUSTAPHA. In a TV show revealed the secret behind the mining of californium in west African country, Nigeria. He also revealed that the mining of californium is also the reason while a particular (borno) state in Nigeria 🇳🇬 experience hight rate of terrorism!.
There are several research that quote that californium does not exist naturally on earth but can be made in the laboratory with the bombarding of curium with helium ions. Now from this context, it shows that there are two elements responsible for californium, which are curium and helium ions. But before i dive in deeper, there are some key words that will convince and prove the existence of californium in Nigeria.
- californium.
- curium.
- helium ions.
- mining.
- Earth crust.
- temperature.
- bombarding.
Californium: this is a chemical element of atomic number 98, a radioactive metal of the actinide series, first produced by bombarding of curium with helium ions. This means that californium is a product of curium and helium after the bombarding process.
Curium: this is a synthetic, radioactive, metallic element with the atomic number of 96. There are many ways and places where curium can be found apart from being produced in the laboratory. But in this contexts, I will focus on environmental samples and nuclear waste ways of finding curium. _ environment sample: trace amounts of Curium can be found in environmental samples such as soil or water, near
nuclear facilities or after nuclear accidents. _ nuclear waste: curium is a component of nuclear waste, particularly in spent nuclear fuel. This means that we can find curium in our environment not only on laboratory.Helium: helium is a chemical element with the atomic number of 2, it is colorless, tasteless, odorless and non toxic, inert monatomic gas. There are ways and places you can get helium but I want to focus on the radioactive decay method of getting helium. _radioactive decay: in this method, helium is produced through the radioactive decay of uranium and thorium in the Earth crust.
Mining: Mining is the process of extracting valuable materials from the beneath the Earth crust, including minerals, metals, and fossil fuels like coal, oil, and gas. It involves various techniques, from digging tunnels for underground mining to excavating open-pit mines. The goal is to locate and extract economically viable deposits of these resources for use in manufacturing, energy production, and other applications.
Temperature: thus is the hotness or coldness of something, which is specifically related to the average kinetic energy of an object's particle. Since particles are in constant motion, they possess kinetic energy, and temperature reflects the energy associated with this particle movement. The temperature beneath the Earth is very high causing this elements (curium and helium) to bombard and form californium 😃.
Bombarding: direct a stream of high-speed particles at (a substance) or element.
Since there are the presence of curium and helium ions beneath the Earth crust, the high temperature beneath there will bombard them both forming californium as the end product, which attracts miners to come do there mining activities and discover californium. 😀
Final, there are atoms of truth in what RTD. AL-MUSTAPHA said about CALIFORNIUM in Nigeria 🇳🇬.
-
 @ 57d1a264:69f1fee1
2025-05-10 05:11:27
@ 57d1a264:69f1fee1
2025-05-10 05:11:27Consider the following two charts from A History of Clojure which detail the introduction and retention of new code by release for both Clojure and for Scala.
While this doesn't necessarily translate to library stability, it's reasonable to assume that the attitude of the Clojure maintainers will seep into the community. And that assumption is true.
Consider a typical Javascript program. What is it comprised of? Objects, objects, and more objects. Members of those objects must be either introspected or divined. Worse, it's normal to monkeypatch those objects, so the object members may (or may not) change over time.
Now, consider a typical Clojure program. What is it comprised of? Namespaces. Those namespaces contain functions and data. Functions may be dynamically generated (via macros), but it is extremely rare to "monkeypatch" a namespace. If you want to know what functions are available in a namespace, you can simply read the source file.
Continue reading https://potetm.com/devtalk/stability-by-design.html
originally posted at https://stacker.news/items/976215
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-16 15:29:10
@ 5d4b6c8d:8a1c1ee3
2025-05-16 15:29:10How could the Dallas Mavericks possibly have gotten the first pick in this draft? League corruption? Mischievous basketball gods? Simulation theory? Dumb stupid luck? Whatever the reason, it's very interesting.
We'll probably be done with the 2nd round, by the time we record, which means round 2 recap and conference finals previews. It's definitely not the matchups anyone expected. What are the implications for our brackets?
The NFL released the season schedules and @grayruby's rightly excited for his 49ers upcoming season.
The parity situation worsens in the MLB, as the Dodgers' pitchers are ravaged by injury. Also, @grayruby and I are going head-to-head in fantasy baseball this week. Who will prevail?
On this week's Blok'd Shots, @grayruby will dance on the Leafs' grave and celebrate their well-deserved misfortune. Hell hath no fury like a scorned Leafs fan. Also, the NHL bracket is coming down to me and @Jer. Will knowing anything about hockey be enough to get Jer the victory?
And, as always, whatever the stackers want us to cover.
https://stacker.news/items/981596
-
 @ d57360cb:4fe7d935
2025-05-16 14:54:18
@ d57360cb:4fe7d935
2025-05-16 14:54:18I soar all over the world, but one of the places I visit often is this little tiny square opening. I land softly on the platform and peer in through the hole. There’s a man inside; he seems to enjoy when I come by. His eyes light up and he gives me crumbs of bread to eat. The bread is tasty and fulfilling; it satisfies my hunger during my flights to other destinations. I wonder what it’s like to be man.
Man does strange things. I can’t fully understand. For example, this man is confined in a tiny box. He sits on what looks like a deformed tree, and in front of him is a tiny rectangular box. Everything man has is so boxy; it’s unnatural to me. When I fly from place to place, I don’t see any boxes; rather, I see a wiggly world. Endless shape, no two things look the same, but to man, it’s like he wants everything to be the same. Man usually is looking at other thin boxes; these are slim and have marks on them. He appears to stare for a long time at them, and then he sets them down and picks up another to stare at. In his box, he has long, narrow boxes. They hold small boxes bundled together with slim boxes. It gives me a headache seeing so many boxes. Once I observed man outside in the wiggly world, and when he left his big box, he went into another smaller box that moved! I was so interested I followed his moving box. You wouldn’t guess where he went to! Another box, but this one was a big one with subsections of smaller boxes. Could you believe they even have big boxes for water! What a headache man is.
The game man plays is interesting; it seems to be about boxes and how to put wiggly things in them. The wiggly is too elusive; one can’t box it up. Even if you surround the wiggly in a box, it will continue to wiggle. Like a tree confined to a planter box, its roots will spread beyond their confinement. Man is like this but believes the box will contain him, shameful.
-
 @ bbef5093:71228592
2025-05-16 17:00:59
@ bbef5093:71228592
2025-05-16 17:00:59Technológiai fejlemények
Az Egyesült Államokban és világszerte jelentős előrelépések történtek a nukleáris technológia területén. A mesterséges intelligencia (AI) egyre nagyobb szerepet kap az atomerőművek működtetésében: például a kaliforniai Diablo Canyon atomerőmű már alkalmaz generatív AI-t a dokumentumkezelés és az üzemeltetési hatékonyság javítására. Az AI segíti az üzemeltetőket a karbantartás előrejelzésében, a biztonság növelésében és a reaktorok élettartamának meghosszabbításában is. Emellett az USA Nukleáris Szabályozó Bizottsága (NRC) is vizsgálja, hogyan gyorsíthatná fel az engedélyezési folyamatokat AI-alapú rendszerekkel, ami jelentősen felgyorsíthatja az új reaktorok telepítését.
A NANO Nuclear Energy jelentős mérföldkövet ért el: megszerezte a KRONOS MMR™ (45 MWth teljesítményű, helyhez kötött mikroreaktor) és a LOKI MMR™ (1–5 MWth teljesítményű, hordozható mikroreaktor) technológiákat, és ezek fejlesztését az USA-ban és Kanadában is előmozdítja. A KRONOS MMR üzemanyag-minősítési módszertanát az NRC már jóváhagyta, ami kulcsfontosságú a kereskedelmi bevezetéshez
Ipari és piaci fejlemények
Az amerikai The Nuclear Company startup 46 millió dolláros tőkebevonással kívánja új, nagy teljesítményű atomerőművek fejlesztését megkezdeni, elsősorban már engedélyezett helyszíneken. A cél, hogy az első flottában összesen 6 gigawatt kapacitást hozzanak létre. Ez a lépés válasz a gyorsan növekvő amerikai áramigényre, amelyet főként az adatközpontok és a mesterséges intelligencia-alkalmazások hajtanak. Ugyanakkor a nukleáris ipar pénzügyi kilátásait bizonytalanság övezi, mivel az amerikai törvényhozás egyes tervezetei a nukleáris energia adókedvezményeinek megszüntetését is kilátásba helyezték, ami a jövőbeni beruházások megtérülését is befolyásolhatja.
Belgiumban a parlament váratlan fordulattal úgy döntött, hogy nem zárják be az atomerőműveket, hanem tíz évvel meghosszabbítják a reaktorok élettartamát, sőt, új reaktorok építését is tervezik. A döntés mögött az energiaválság, az ellátásbiztonság és a geopolitikai feszültségek állnak.
Magyarországon folytatódik a Paks II. projekt előkészítése, és napirenden van kis moduláris reaktorok (SMR) telepítése is, amelyek néhány száz megawattos teljesítményükkel akár ipari zónákat vagy városokat is önállóan elláthatnak.
Pénzügyi és geopolitikai aktualitások
A nukleáris energia geopolitikai jelentősége továbbra is kiemelkedő. Tajvan szombaton leállítja utolsó működő atomerőművi blokkját, ami jelentős LNG-import költségnövekedést eredményez, és komoly vitákat váltott ki a szigetországban. A törvényhozás ugyanakkor már vizsgálja az atomenergia-törvény felülvizsgálatát, amely lehetővé teheti a reaktorok újraindítását – erről akár népszavazás is lehet a közeljövőben.
Az USA és Irán között folytatódnak az atomprogramról szóló tárgyalások. Bár közelednek az álláspontok, az USA új szankciókat vezetett be Irán ellen, mivel Teherán továbbra is magas szintű urándúsítást folytat. Az esetleges megállapodás rövid távon növelheti az iráni kőolajexportot, ami a világpiaci árakra is hatással lehet.
-
 @ 57d1a264:69f1fee1
2025-05-08 05:25:48
@ 57d1a264:69f1fee1
2025-05-08 05:25:48Safe Bits & Self Custody Tips
The journey of onboarding a user and create a bitcoin multiSig setup begins far before opening a desktop like Bitcoin Safe (BS) or any other similar application. Bitcoin Safe seems designed for families and people that want to start exploring and learning about multiSig setup. The need for such application and use of it could go much further, defining best practices for private organizations that aim to custody bitcoin in a private and anonymous way, following and enjoy the values and standards bitcoin has been built for.
Intro
Organizations and small private groups like families, family offices and solopreneurs operating on a bitcoin standard will have the need to keep track of transactions and categorize them to keep the books in order. A part of our efforts will be spent ensuring accessibility standards are in place for everyone to use Bitcoin Safe with comfort and safety.
We aim with this project to bring together the three Designathon ideas below: - Bitcoin Safe: improve its overall design and usability. - No User Left Behind: improve Bitcoin Safe accessibility. - Self-custody guidelines for organizations: How Bitcoin Safe can be used by private organization following best self-custody practices.
We are already halfway of the first week, and here below the progress made so far.
Designing an icon Set for Bitcoin Safe
One of the noticeable things when using BS is the inconsistency of the icons, not just in colors and shapes, but also the way are used. The desktop app try to have a clean design that incorporate with all OS (Win, macOS, Linux) and for this reason it's hard to define when a system default icon need to be used or if a custom one can be applied instead. The use of QT Ui framework for python apps help to respond to these questions. It also incorporates and brig up dome default settings that aren't easily overwritten.
Here below you can see the current version of BS:
Defining a more strict color palette for Bitcoin Safe was the first thing!
How much the icons affect accessibility? How they can help users to reach the right functionality? I took the challenge and, with PenPot.app, redesigned the icons based on the grid defined in the https://bitcoinicons.com/ and proposing the implementation of it to have a cleaner and more consistent look'n feel, at least for the icons now.
What's next
I personally look forward to seeing these icons implemented soon in Bitcoin Safe interface. In the meantime, we'll focus on delivering an accessibility audit and evaluate options to see how BS could be used by private organizations aiming to become financially sovereign with self-custody or more complex bitcoin multiSig setups.
One of the greatest innovations BS is bringing to us is the ability to sync the multiSig wallets, including PBST, Categories and labels, through the nostr decentralized protocol, making current key custodial services somehow obsolete. Second-coolest feature that this nostr implementation brings is the ability to have a build-in private chat that connect and enable the various signers of a multiSig to communicate and sign transactions remotely. Where have you seen something like this before?
Categories UX and redesign is also considered in this project. We'll try to understand how to better serve this functionality to you, the user, really soon.
Stay tuned!
originally posted at https://stacker.news/items/974488
-
 @ f85b9c2c:d190bcff
2025-05-16 14:23:39
@ f85b9c2c:d190bcff
2025-05-16 14:23:39 I used to think I thrived on chaos. Podcasts blaring, TV on in the background, notifications pinging—it was my norm. But last year, I hit a wall. I was irritable, foggy, and couldn’t focus. I didn’t realize how much the constant noise was frying my brain until I tried something radical: silence.
I used to think I thrived on chaos. Podcasts blaring, TV on in the background, notifications pinging—it was my norm. But last year, I hit a wall. I was irritable, foggy, and couldn’t focus. I didn’t realize how much the constant noise was frying my brain until I tried something radical: silence.The Experiment One weekend, I turned everything off. No music, no screens, no chatter. At first, it was weird—almost suffocating. My mind raced, looking for something to latch onto. But after a few hours, I settled in. I sat with a cup of tea, just listening to the hum of the fridge. It was the first time in months I’d actually heard my own thoughts
What Silence Gave Me That quiet weekend was a reset. I started noticing things I’d ignored—like how tense I’d been or how I’d been avoiding tough decisions. Silence didn’t just calm me; it forced me to face myself. I kept it up, carving out 30 minutes a day with no sound. It’s become my sanity-saver. When life gets loud, those quiet moments keep me grounded. Turns out, my brain needed the break. All that noise was overloading me, leaving no room to process anything. Silence let me recharge and think clearly again. It’s not about being a hermit—it’s about giving myself space to breathe.
-
 @ 57d1a264:69f1fee1
2025-05-08 05:08:36
@ 57d1a264:69f1fee1
2025-05-08 05:08:36Welcome back to our weekly
JABBB, Just Another Bitcoin Bubble Boom, a comics and meme contest crafted for you, creative stackers!If you'd like to learn more, check our welcome post here.
This week sticker:
Bitcoin SirYou can download the source file directly from the HereComesBitcoin website in SVG and PNG. Use this sticker around SN with the code
The task
Make sure you use this week sticker to design a comic frame or a meme, add a message that perfectly captures the sentiment of the current most hilarious takes on the Bitcoin space. You can contextualize it or not, it's up to you, you chose the message, the context and anything else that will help you submit your comic art masterpiece.
Are you a meme creator? There's space for you too: select the most similar shot from the gifts hosted on the Gif Station section and craft your best meme... Let's Jabbb!
If you enjoy designing and memeing, feel free to check out the JABBB archive and create more to spread Bitcoin awareness to the moon.
Submit each proposal on the relative thread, bounties will be distributed when enough participants submit options.
PS: you can now use HereComesBitcoin stickers to use on Stacker.News
₿e creative, have fun! :D
originally posted at https://stacker.news/items/974483
-
 @ f85b9c2c:d190bcff
2025-05-16 14:08:51
@ f85b9c2c:d190bcff
2025-05-16 14:08:51 In the rapidly evolving world of cryptocurrencies, the potential interplay between artificial intelligence and digital assets has captured significant attention. Cointelegraph recently reported on the concept of AI, particularly in the form of ChatGPT, contributing to the potential rise of Bitcoin, potentially reaching a value of $100K in 2024. This development offers a glimpse into the role of AI in shaping the direction of cryptocurrencies, particularly Bitcoin.
In the rapidly evolving world of cryptocurrencies, the potential interplay between artificial intelligence and digital assets has captured significant attention. Cointelegraph recently reported on the concept of AI, particularly in the form of ChatGPT, contributing to the potential rise of Bitcoin, potentially reaching a value of $100K in 2024. This development offers a glimpse into the role of AI in shaping the direction of cryptocurrencies, particularly Bitcoin.AI’s Role in Shaping Bitcoin’s Future: ChatGPT, an advanced language model powered by artificial intelligence, has been seen as a potential assistant in driving Bitcoin’s value upwards. The underlying premise is rooted in AI’s capacity to influence market analysis, comprehend and design trading strategies, and anticipate potential trends in the cryptocurrency sector. By leveraging vast amounts of data and analyzing complex patterns, ChatGPT could provide insights that impact investment decisions and market.
AI-Powered Market Analysis and Prediction One of the key ways AI, represented by ChatGPT, can aid Bitcoin’s value appreciation is through advanced market analysis and prediction. By assimilating and processing large datasets encompassing historical price movements, trading volumes, market sentiment, and external factors, AI can potentially forecast potential price changes with a higher degree of accuracy. This analytical capability could equip investors with valuable insights regarding optimal entry and exit points, thus potentially contributing to Bitcoin’s upward trajectory. Furthermore, AI’s predictive abilities extend to discerning macroeconomic and geopolitical developments that could impact Bitcoin’s value, enabling proactive decision-making in response to dynamic market conditions. This foresight could instill confidence among investors and potentially drive greater adoption and investment in Bitcoin, which contributed to its ascent $100K mark.
Influencing Trading Strategies AI-driven trading strategies have gained prominence in financial markets, and their potential impact on Bitcoin’s valuation is noteworthy. ChatGPT’s capacity to generate and optimize trading algorithms that respond to market conditions in real-time could potentially enhance trading efficiency and liquidity in Bitcoin markets. By identifying opportunities for arbitrage, risk management, and executing complex trading strategies, AI could facilitate a more stable and robust Bitcoin market, potentially attracting institutional investors and bolstering its overall value.
Market Volatility Volatility has been a defining characteristic of the cryptocurrency markets, including Bitcoin. AI, through ChatGPT, could aid in mitigating this volatility by providing real-time insights, sentiment analysis, and risk assessments to market participants. By enhancing transparency and reducing uncertainty, AI-driven tools may contribute to a more stable and predictable environment for Bitcoin trading, potentially attracting a broader investor base and positively influencing its long-term value, including the speculated $100K threshold. Conclusion The potential for AI, exemplified by ChatGPT, to influence Bitcoin’s trajectory towards a $100K valuation in 2024 underscores the evolving synergy between technology and finance. As AI continues to permeate various domains, its impact on cryptocurrency markets is poised to be substantial. It is imperative to monitor the evolution of AI’s role in shaping the future of Bitcoin and other digital assets, as it has the potential to redefine investment strategies, market dynamics, and the broader financial landscape in the years to come.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28IPFS problems: Conceit
IPFS is trying to do many things. The IPFS leaders are revolutionaries who think they're smarter than the rest of the entire industry.
The fact that they've first proposed a protocol for peer-to-peer distribution of immutable, content-addressed objects, then later tried to fix that same problem using their own half-baked solution (IPNS) is one example.
Other examples are their odd appeal to decentralization in a very non-specific way, their excessive flirtation with Ethereum and their never-to-be-finished can-never-work-as-advertised Filecoin project.
They could have focused on just making the infrastructure for distribution of objects through hashes (not saying this would actually be a good idea, but it had some potential) over a peer-to-peer network, but in trying to reinvent the entire internet they screwed everything up.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28notes on "Economic Action Beyond the Extent of the Market", Per Bylund
Source: https://www.youtube.com/watch?v=7St6pCipCB0
Markets work by dividing labour, but that's not as easy as it seems in the Adam Smith's example of a pin factory, because
- a pin factory is not a market, so there is some guidance and orientation, some sort of central planning, inside there that a market doesn't have;
- it is not clear how exactly the production process will be divided, it is not obvious as in "you cut the thread, I plug the head".
Dividing the labour may produce efficiency, but it also makes each independent worker in the process more fragile, as they become dependent on the others.
This is partially solved by having a lot of different workers, so you do not depend on only one.
If you have many, however, they must agree on where one part of the production process starts and where it ends, otherwise one's outputs will not necessarily coincide with other's inputs, and everything is more-or-less broken.
That means some level of standardization is needed. And indeed the market has constant incentives to standardization.
The statist economist discourse about standardization is that only when the government comes with a law that creates some sort of standardization then economic development can flourish, but in fact the market creates standardization all the time. Some examples of standardization include:
- programming languages, operating systems, internet protocols, CPU architectures;
- plates, forks, knifes, glasses, tables, chairs, beds, mattresses, bathrooms;
- building with concrete, brick and mortar;
- money;
- musical instruments;
- light bulbs;
- CD, DVD, VHS formats and others alike;
- services that go into every production process, like lunch services, restaurants, bakeries, cleaning services, security services, secretaries, attendants, porters;
- multipurpose steel bars;
- practically any tool that normal people use and require a little experience to get going, like a drilling machine or a sanding machine; etc.
Of course it is not that you find standardization in all places. Specially when the market is smaller or new, standardization may have not arrived.
There remains the truth, however, that division of labour has the potential of doing good.
More than that: every time there are more than one worker doing the same job in the same place of a division of labour chain, there's incentive to create a new subdivision of labour.
From the fact that there are at least more than one person doing the same job as another in our society we must conclude that someone must come up with an insight about an efficient way to divide the labour between these workers (and probably actually implement it), that hasn't happened for all kinds of jobs.
But to come up with division of labour outside of a factory, some market actors must come up with a way of dividing the labour, actually, determining where will one labour stop and other start (and that almost always needs some adjustments and in fact extra labour to hit the tips), and also these actors must bear the uncertainty and fragility that division of labour brings when there are not a lot of different workers and standardization and all that.
In fact, when an entrepreneur comes with a radical new service to the market, a service that does not fit in the current standard of division of labour, he must explain to his potential buyers what is the service and how the buyer can benefit from it and what he will have to do to adapt its current production process to bear with that new service. That's has happened not long ago with
- services that take food orders from the internet and relay these to the restaurants;
- hostels for cheap accommodation for young travellers;
- Uber, Airbnb, services that take orders and bring homemade food from homes to consumers and similars;
- all kinds of software-as-a-service;
- electronic monitoring service for power generators;
- mining planning and mining planning software; and many other industry-specific services.
See also
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Veterano não é dono de bixete
"VETERANO NÃO É DONO DE BIXETE". A frase em letras garrafais chama a atenção dos transeuntes neófitos. Paira sobre um cartaz amarelo que lista várias reclamações contra os "trotes machistas", que, na opinião do responsável pelo cartaz, "não é brincadeira, é opressão".
Eis aí um bizarro exemplo de como são as coisas: primeiro todos os universitários aprovam a idéia do trote, apoiam sua realização e até mesmo desejam sofrer o trote -- com a condição de o poderem aplicar eles mesmos depois --, louvam as maravilhas do mundo universitário, onde a suprema sabedoria se esconde atrás de rituais iniciáticos fora do alcance da imaginação do homem comum e rude, do pobre e do filhinho-de-papai das faculdades privadas; em suma: fomentam os mais baixos, os mais animalescos instintos, a crueldade primordial, destroem em si mesmos e nos colegas quaisquer valores civilizatórios que tivessem sobrado ali, ficando todos indistingüíveis de macacos agressivos e tarados.
Depois vêm aí com um cartaz protestar contra os assédios -- que sem dúvida acontecem em larguíssima escala -- sofridos pelas calouras de 17 anos e que, sendo também novatas no mundo universitário, ainda conservam um pouco de discernimento e pudor.
A incompreensão do fenômeno, porém, é tão grande, que os trotes não são identificados como um problema mental, uma doença que deve ser tratada e eliminada, mas como um sintoma da opressão machista dos homens às mulheres, um produto desta civilização paternalista que, desde que Deus é chamado "o Pai" e não "a Mãe", corrompe a benéfica, pura e angélica natureza do homem primitivo e o torna esta tão torpe criatura.
Na opinião dos autores desse cartaz é preciso, pois, continuar a destruir o que resta da cultura ocidental, e então esperar que haja trotes menos opressores.
-
 @ e39333da:7c66e53a
2025-05-16 13:20:33
@ e39333da:7c66e53a
2025-05-16 13:20:33::youtube{#Pex7jW3Tqwo}
Developer SHIFT UP has announced that their latest titled, Stellar Blade, that was released on PS5 on the 2024, will release on PC via Steam and EGS on the 11th of June 2025.
The game will be priced at $60, and $80 for the edition of the game that includes the 'Twin Expansion Pack', which includes the NieR: Automata DLC and the Goddess of Victory: Nikke DLC, and a key to redeem a Stellar Blade costume in the developer's previous Free-to-Play title Goddess of Victory: Nikke.
The trailer released to announce said release date also showcases the changes the made for the game and highlight PC specific enhancements, support, and options.
It's worth noting, in terms of negative news that tagged along with this, that the game will have Denuvo running, which there are evidence that decreases a game's performance, and may prevent you from playing the game offline. The game will also have an optional PSN account login, and because of this, the game is not available for purchase in around 130 countries. There's also an exclusive outfit locked behind a PSN-to-Steam account linking.

Here's the system requirements:
| | Minimum | Recommended | High | Very High | | ----------------------- | ----------------------------------------------------- | ------------------------------------------------------- | ------------------------------------------------------- | ------------------------------------------------- | | Average Performance | 1080P at 60 frames per second | 1440P at 60 frames per second | 1440P at 60 frames per second | 4K at 60 frames per second | | Graphic Presets | Low | Medium | High | Very High | | CPU | Intel Core i5-7600K AMD Ryzen 5 1600X | Intel Core i5-8400 AMD Ryzen 5 3600X | Intel Core i5-8400 AMD Ryzen 5 3600X | Intel Core i5-8400 AMD Ryzen 5 3600X | | GPU | NVIDIA GeForce GTX 1060 6GB AMD Radeon RX 580 8GB | NVIDIA GeForce RTX 2060 SUPER AMD Radeon RX 5700 XT | NVIDIA GeForce RTX 2070 SUPER AMD Radeon RX 6700 XT | NVIDIA GeForce RTX 3080 AMD Radeon RX 7900 XT | | RAM | 16GB | 16GB | 16GB | 16GB | | Storage | 75GB HDD (SSD Recommended) | 75GB SSD | 75GB SSD | 75GB SSD | | OS | Windows 10 64-bit | Windows 10 64-bit | Windows 10 64-bit | Windows 10 64-bit |
-
 @ 57d1a264:69f1fee1
2025-05-07 06:56:25
@ 57d1a264:69f1fee1
2025-05-07 06:56:25Wild parrots tend to fly in flocks, but when kept as single pets, they may become lonely and bored https://www.youtube.com/watch?v=OHcAOlamgDc
Source: https://www.smithsonianmag.com/smart-news/scientists-taught-pet-parrots-to-video-call-each-other-and-the-birds-loved-it-180982041/
originally posted at https://stacker.news/items/973639
-
 @ 57d1a264:69f1fee1
2025-05-07 06:29:52
@ 57d1a264:69f1fee1
2025-05-07 06:29:52Your device, your data. TRMNL's architecture prevents outsiders (including us) from accessing your local network. TRMNAL achieve this through 1 way communication between client and server, versus the other way around. Learn more.
Learn more at https://usetrmnl.com/
originally posted at https://stacker.news/items/973632
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28A crappy zk-rollups explanation attempt
(Considering the example of zksync.io) (Also, don't believe me on any of this.)
- They are sidechains.
- You move tokens to the sidechain by depositing it on an Ethereum contract. Then your account is credited in the sidechain balance.
- Then you can make payments inside the sidechain by signing transactions and sending them to a central operator.
- The central operator takes transactions from a bunch of people, computes the new sidechain balances state and publishes a hash of that state to the Ethereum contract.
- The idea is that a single transaction in the blockchain contains a bunch of sidechain transactions.
- The operator also sends to the contract an abbreviated list of the sidechain transactions. The trick is making all signatures condensed in a single zero-knowledge proof which is enough for the contract to verify that the transition from the previous state to the new is good.
- Apparently they can fit 500 sidechain transactions in one mainchain transaction (each is 12 bytes). So I believe it's fair to say all this zk-rollup fancyness could be translated into "a system for aggregating transactions".
-
I don't understand how the zero-knowledge proof works, but in this case it is a SNARK and requires a trusted setup, which I imagine is similar to this one.
-
 @ 4fa5d1c4:fd6c6e41
2025-05-16 13:15:47
@ 4fa5d1c4:fd6c6e41
2025-05-16 13:15:47Willkommen zur Mitmachplattform: KI-Kompetenzen für die religionsbezogene Bildung
Diese Plattform ist ein offenes, gemeinschaftliches Lernmodul für alle, die KI-Kompetenzen im Kontext der religionsbezogenen Bildung entdecken, vertiefen und weitergeben möchten.
Hier können Religionslehrende, Hochschulangehörige und ehrenamtlich Engagierte gemeinsam Inhalte entwickeln, teilen und weiterentwickeln.
Was ist das Ziel?
Wir schaffen eine offene Lernumgebung, in der Materialien zu KI-Kompetenzen für Schule, Hochschule und außerschulische Jugendarbeit kollaborativ entstehen.
Die Plattform richtet sich an Lehrkräfte, Fortbildner:innen und Ehrenamtliche, die KI-Themen in der religiösen Bildung verantwortungsvoll erschließbar machen wollen.
Unser Kompetenzmodell
Im Zentrum steht ein Kreismodell mit vier Kompetenzbereichen, die auf drei Niveaustufen ausdifferenziert sind:
Verstehen, Anwenden, Reflektieren und Gestalten.
Diese Bereiche bauen aufeinander auf, beeinflussen sich gegenseitig und werden durch die zentrale Kompetenz AI Leadership verbunden.Im Zentrum steht ein Kreismodell mit vier Kompetenzbereichen, die auf drei Niveaustufen ausdifferenziert werden können:
Verstehen, Anwenden, Reflektieren und Gestalten.
Diese Bereiche bauen aufeinander auf, beeinflussen sich gegenseitig und werden durch die zentrale Kompetenz AI Leadership verbunden.| Kompetenzbereich | Beschreibung | |------------------|--------------| | 🟢 VERSTEHEN | Grundlagen und Mechanismen von KI | | 🔵 ANWENDEN | KI-Tools im Lernprozess nutzen | | 🟠 REFLEKTIEREN | Kritische Auseinandersetzung mit KI | | 🟣 GESTALTEN | Aktive Weiterentwicklung von KI-Systemen |
Jeder Lerninhalt ist einem Kompetenzbereich (und wenn möglich einer Niveaustufe) zugeordnet – farblich und inhaltlich klar erkennbar.
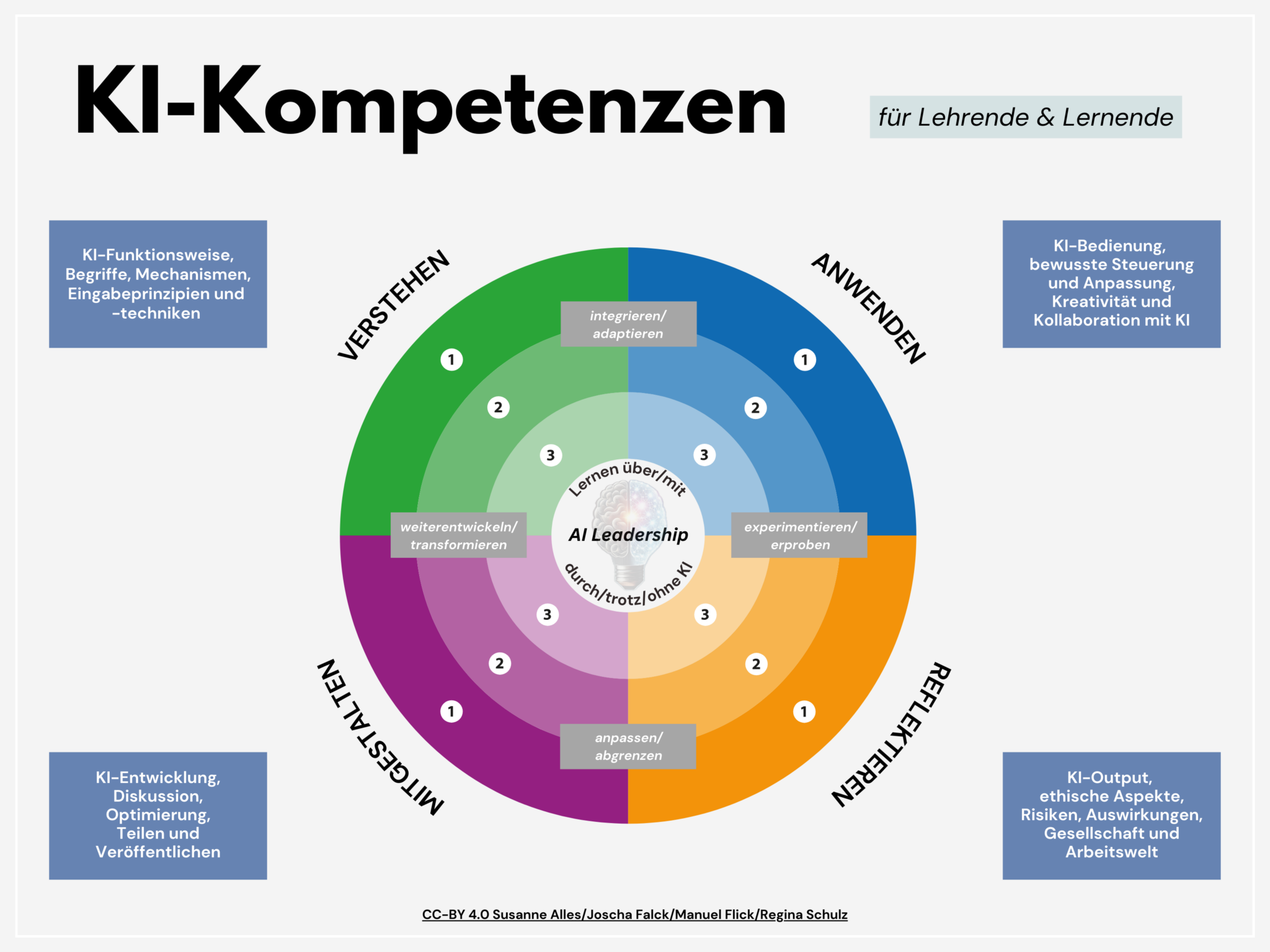
So funktioniert die Mitmachplattform
- Offene Inhalte: Alle Materialien werden als Markdown-Dateien über Nostr gepflegt.
- Mitmachen leicht gemacht: Egal wo auf Nostr du publizierst, mit den Hashtags #relilab und dem jeweiligen Kompetenzbereich als Schlagwort (also #verstehen, #anwenden, #gestalten, #reflektieren) finden wir diese Hashtagkombination und können die Webseite mit deiner Idee oder Weiterentwicklung ergänzen.
- Anleitungen: Eine eigene Seite erklärt Schritt für Schritt, wie du dich beteiligen kannst – ganz ohne Vorkenntnisse im Programmieren.
- Suchfunktion: Finde gezielt Inhalte nach Kompetenzbereich, Niveaustufe oder Schlagworten.
Für wen ist diese Plattform?
- Lehrkräfte an Schulen und Hochschulen in religionsbezogenen Fächern
- Ehrenamtliche und Multiplikator:innen in der kirchlichen Jugendarbeit
- Fort- und Weiterbildner:innen im Bereich KI und Religion
Mitmachen & Teilen
"Sharing is Caring":
Unser KI-Kompetenzmodell und alle Lernmaterialien stehen unter der offenen Lizenz [CC-BY 4.0].
Du darfst sie frei nutzen, anpassen und weitergeben – mit Nennung der Urheber:innen.
Starte jetzt!
Gemeinsam gestalten wir KI-Kompetenzen für eine reflektierte, verantwortungsvolle und kreative religiöse Bildung im KI-Zeitalter.
Kontakt & Feedback:
Für Fragen, Anregungen oder Feedback antworte einfach auf diese Nachricht oder komm' in den Matrix/Element-Raum #relilab-ki:rpi-virtuell zum Online-Austausch! -
 @ 57d1a264:69f1fee1
2025-05-07 06:16:30
@ 57d1a264:69f1fee1
2025-05-07 06:16:30Here’s Sean Voisen writing about how programming is a feeling:
For those of us who enjoy programming, there is a deep satisfaction that comes from solving problems through well-written code, a kind of ineffable joy found in the elegant expression of a system through our favorite syntax. It is akin to the same satisfaction a craftsperson might find at the end of the day after toiling away on well-made piece of furniture, the culmination of small dopamine hits that come from sweating the details on something and getting them just right. Maybe nobody will notice those details, but it doesn’t matter. We care, we notice, we get joy from the aesthetics of the craft.
This got me thinking about the idea of satisfaction in craft. Where does it come from?
Continue Reading https://blog.jim-nielsen.com/2025/craft-and-satisfaction/
originally posted at https://stacker.news/items/973628
-
 @ 84b0c46a:417782f5
2025-05-16 13:09:31
@ 84b0c46a:417782f5
2025-05-16 13:09:31₍ ・ᴗ・ ₎ ₍ ・ᴗ・ ₎₍ ・ᴗ・ ₎
-
 @ 88cc134b:5ae99079
2025-05-16 19:04:30
@ 88cc134b:5ae99079
2025-05-16 19:04:30text
-
 @ 87fedb9f:0da83419
2025-05-16 12:45:01
@ 87fedb9f:0da83419
2025-05-16 12:45:01Push it! Push it! Push it!
That chant still echoes in my bones, not just from the gym, but from the inside out. I remember watching a bodybuilder once — the weight trembling above him, his muscles bulging and giving out, the spotters swooping in to catch the bar just in time. “Train to failure,” they said. “That’s how you grow.”
And it makes sense, doesn’t it? If you’re being chased by a wild beast, you run until your body gives out. That’s how we’re wired — to survive first and foremost, not necessarily to thrive.
But what if the house we’re building isn’t under threat from wolves? What if we’ve got stone-moving machines and time to breathe? What if we’re not being chased anymore… but we still act like we are?
See, survival patterns are sneaky. They wear masks. They show up in workouts and work days. They dress up in ambition, caffeine, and “just one more thing before I stop.”
I’ve never been a bodybuilder — my brother was — but I’ve tried that route in my own work life. Lift to failure. Push it. Every other day, I’d be nursing another injury to body and mind.
I wasn’t getting stronger. I was just breaking myself in cycles. Push, break, recover, repeat.
I see the same thing with brains. Push it. Adderall. More coffee. Keep going. Hit the wall. And then—collapse.
That’s not strengthening. That’s surviving pretending to be “powerful.”
What happens to the rest of your system when your brain is sucking up all the energy just to stay on task? You stop digesting. You stop feeling the sun on your skin. You stop enjoying your kids’ laughter. Everything feels like something to push through.
That isn’t thriving.
Thriving feels different. It’s alive, yes — there’s activation. But it’s not strained. When we’re in thriving mode, we’re with our energy, not yanking it out by the roots and forcing it to regrow. The muscles — or the mind — are engaged, fluid, expressive. Alive.
It’s a fine line. You can take the same exact action and fill it with stress.
I’ve done it. I’ve turned a perfectly normal task into a survival sprint. It feels ridiculous in hindsight — like, why did I make this email reply into a mountain climb?
Because my primitive brain still whispers, “If you don’t do this perfectly and fast, you’ll die.” Not literally. But the threat feels real. The imagined judgment, the self-criticism, the fear of not being enough — they’re imaginary lions in the tall grass of modern life.
I’ve used this system on myself. I’ve strained my nervous system like fingernails scraping rock to avoid a fall that was never coming.
That’s what we’re supposed to do, right? We bring survival force into every aspect. Into parenting. Into projects. Into relationships.
And we wonder why we’re tired all the time. Not sleepy tired — soul tired. That kind of tired that feels like you ran for your life… but all you did was sit at your desk.
Here’s what I know now: if you’re not actually in danger, you can stop living like you are.
You don’t have to push everything to the edge. You don’t have to prove your strength through strain. Strength can be alive in you — not torn, not depleted, but awake and sustaining.
And when we live from there, the recovery feels different, too. We’re not collapsing. We’re restoring.
We’re not dropping all the pieces and then forcing ourselves to pick them up… again! Instead, we’re crafting a thriving life from the pieces we find, fashion, and consciously put in place.
There’s a wisdom to building your foundation around thriving — not just surviving. And thriving starts with recognizing: it’s not life or death to get through your inbox. Your self-worth isn’t measured by how busy and depleted you are.
Look around. Are you stacking more and more iron to prove something? Or are you listening to the quiet whisper that says, “Yes, move… but don’t hurt yourself doing it.”
And in a life that tells you to push until you fail, choosing to rest and relish — choosing to feel alive rather than just alive-enough — might just be the truest strength there is.
Useful Concepts for Thriving in This Story
-
Primitive Brain\ The primitive brain keeps us on high alert even when we’re safe — it’s time to question whether the lion is real.
-
Unrushed\ Being unrushed is a radical shift from survival tempo to the rhythm of true aliveness.
-
Savvy\ Savvy invites us to work with our energy wisely, not destructively — to choose thriving over proving.
-
Vitality\ Vitality flows when we stop draining ourselves for performance and start living from inner strength.
-
Inspired Action\ Inspired action arises from presence and aliveness, not adrenaline and depletion.
-
-
 @ 8f69ac99:4f92f5fd
2025-05-16 11:40:35
@ 8f69ac99:4f92f5fd
2025-05-16 11:40:35Há algo quase reconfortante na previsibilidade com que certos colunistas abordam Bitcoin: a cada oportunidade, repetem os mesmos chavões, reciclados com indignação moralista e embrulhados numa embalagem de falsa autoridade. O artigo publicado na Visão, com o título dramático "De criança prodígio a adolescente problemático", encaixa-se perfeitamente nesse molde.
Trata-se de uma peça de opinião que mistura factos irrelevantes com interpretações enviesadas, estatísticas sem contexto e um medo mal disfarçado de perder o monopólio da narrativa económica. A autora, Sofia Santos Machado, opta por colar em Bitcoin os desastres do chamado “mundo cripto” como se fossem parte do mesmo fenómeno — ignorando, por conveniência ou ignorância, que Bitcoin não é altcoins, não é NFTs, não é esquemas de yield exótico, e não é fintech vestida de blockchain.
Esta resposta centra-se exclusivamente em Bitcoin — um protocolo monetário aberto, incorruptível e resistente à censura, que já está a servir como salvaguarda de valor em regiões onde o sistema financeiro convencional falhou. Não me interessa defender pirâmides, tokens inflacionários ou aventuras bancárias mal calculadas.
Criticar Bitcoin é legítimo — mas fazê-lo sem saber do que se fala é apenas desinformação.
A Histeria da Água — Falar Sem Saber
O artigo abre com uma pérola alarmista sobre o consumo de água:
“Uma única transacção de bitcoin consome seis milhões de vezes mais água do que um pagamento com cartão.”
Seis. Milhões. De vezes. Resta saber se a autora escreveu isto com cara séria ou a rir-se enquanto bebia água engarrafada dos Alpes Suíços.
Fontes? Metodologia? Contexto? Estou a brincar — isto é a Visão, onde os números são decoração e os factos opcionais.
Claro que comparar transacções na camada base de Bitcoin com pagamentos "instantâneos" da rede Visa é tão rigoroso como comparar um Boeing 747 com um avião de papel porque um voa mais longe. Um artigo sério teria falado em batching, na Lightning Network, ou no facto de que Bitcoin nem sequer compete com a Visa nesse nível, nem em nenhum. Mas isso exigiria, imagine-se, investigação.
Pior ainda, não há qualquer menção ao consumo de água na extracção de ouro, nos data centers bancários, ou no treino de modelos de inteligência artificial. Pelos vistos, só Bitcoin tem de obedecer aos mandamentos ecológicos da Visão. O resto? Santa ignorância selectiva.
Criminosos e o Fantasma do Satoshi
Eis o clássico: “Bitcoin é usado por criminosos”. Um cliché bafiento tirado do baú de 2013, agora reapresentado como se fosse escândalo fresco.
Na realidade, Bitcoin é pseudónimo, não anónimo. Todas as transacções ficam gravadas num livro público — não é propriamente o esconderijo ideal para lavar dinheiro, a menos que sejas fã de disfarces em néon.
E os dados? Claríssimos. Segundo a Chainalysis e a Europol, a actividade ilícita com Bitcoin tem vindo a diminuir. Enquanto isso, os bancos — esses bastiões de confiança — continuam a ser apanhados a lavar biliões para cartéis e cleptocratas. Mas disso a Visão não fala. Devia estragar a narrativa.
O verdadeiro crime aqui é a preguiça intelectual tão profunda que quase merece uma moldura. A Visão tem um editor?
O Espantalho Energético
Como uma criança que acabou de aprender uma palavra nova, a Visão repete “consumo energético” como se fosse um pecado original. Bitcoin usa electricidade — escândalo!
Mas vejamos: o Proof-of-Work não é um defeito. É a razão pela qual Bitcoin é seguro. Não há “desperdício” — há uso, e muitas vezes com energia excedente, renovável, ou que de outro modo seria desperdiçada. É por isso que os mineiros se instalam junto a barragens remotas, queima de gás (flaring), ou parques eólicos no meio do nada — não porque odeiam o planeta, mas porque os incentivos económicos funcionam. Escrevi sobre isso aqui.
O que a Visão convenientemente ignora é que Bitcoin está a ajudar a integrar mais energia renovável nas redes, funcionando como carga flexível. Mas nuance? Trabalho de casa? Esquece lá isso.
Para uma explicação mais séria, podiam ter ouvido o podcast A Seita Bitcoin com o Daniel Batten. Mas para quê investigar?
Cripto = Bitcoin = Fraude?
Aqui chegamos ao buraco negro intelectual: enfiar tudo no mesmo saco. FTX colapsou? Culpa de Bitcoin. Um banqueiro jogou com altcoins? Culpa de Bitcoin. Scam de NFT? Deve ter sido o Satoshi.
Vamos esclarecer: Bitcoin não é “cripto”. Bitcoin é descentralizado, sem líderes, transparente. Não teve pré-mineração, não tem CEO, não promete lucros. O que o rodeia? Tokens centralizados, esquemas Ponzi, pirâmides e vaporware — precisamente o oposto do que Bitcoin representa.
Se um executivo bancário perde o dinheiro dos clientes em Dogecoins, isso é um problema dele. Bitcoin não lhe prometeu nada. Foi a ganância.
E convenhamos: os bancos tradicionais também colapsam. E não precisam de satoshis para isso. Bastam dívidas mal geridas, contabilidade criativa e uma fé cega no sistema.
Culpar Bitcoin por falcatruas “cripto” é como culpar o TCP/IP ou SMTP por emails de phishing. É preguiçoso, desonesto e diz-nos mais sobre a autora do que sobre a tecnologia.
Promessas Por Cumprir? Só Se Não Estiveres a Ver
A "jornalista" da Visão lamenta que “após 15 anos, os riscos são reais mas as promessas por cumprir”. Que promessas? Dinheiro grátis? Cafés pagos com QR codes mágicos?
Bitcoin nunca prometeu fazer cappuccinos mais rápidos. Prometeu soberania monetária, resistência à censura e um sistema previsível. E tem cumprido — diariamente, para milhões. E para o cappuccino, há sempre a Lightning Network.
Pergunta aos venezuelanos, nigerianos, peruanos ou argentinos se Bitcoin falhou. Para muitos, é a única forma de escapar à hiperinflação, ao confisco estatal e à decadência financeira.
Bitcoin não é uma app. É infra-estrutura. É uma nova camada base para o dinheiro global. Não se vê — mas protege, impõe regras e não obedece a caprichos de banqueiros centrais.
E isso assusta. Especialmente quem nunca viveu fora da bolha do euro.
Conclusão: A Visão a Gritar Contra o Progresso
No fim, o artigo da Visão é um festival de clichés, dados errados e ressentimento. Não é só enganador. É desonesto. Culpa a tecnologia pelos erros dos homens. Rejeita o futuro em nome do conforto passado.
Bitcoin não é uma varinha mágica. Mas é a fundação de uma nova liberdade financeira. Uma ferramenta para proteger valor, resistir a abusos e escapar ao controlo constante de quem acha que sabe o que é melhor para ti.
Portanto, fica aqui o desafio, Sofia: se queres criticar Bitcoin, primeiro percebe o que é. Lê o white paper. Estuda. Faz perguntas difíceis.
Caso contrário, és só mais um cão a ladrar para a trovoada — muito barulho, zero impacto.
-
 @ 57d1a264:69f1fee1
2025-05-07 06:03:29
@ 57d1a264:69f1fee1
2025-05-07 06:03:29CryptPad
Collaboration and privacy. Yes, you can have both Flagship instance of CryptPad, the end-to-end encrypted and open-source collaboration suite. Cloud administered by the CryptPad development team. https://cryptpad.fr/
ONLYOFFICE DocSpace
Document collaboration made simpler. Easily collaborate with customizable rooms. Edit any content you have. Work faster using AI assistants. Protect your sensitive business data. Download or try STARTUP Cloud (Limited-time offer) FREE https://www.onlyoffice.com/
SeaFile
A new way to organize your files Beyond just syncing and sharing files, Seafile lets you add custom file properties and organize your files in different views. With AI-powered automation for generating properties, Seafile offers a smarter, more efficient way to manage your files. Try it Now, Free for up to 3 users https://seafile.com/
SandStorm
An open source platform for self-hosting web apps Self-host web-based productivity apps easily and securely. Sandstorm is an open source project built by a community of volunteers with the goal of making it really easy to run open source web applications. Try the Demo or Signup Free https://alpha.sandstorm.io/apps
NextCloud Hub
A new generation of online collaboration that puts you in control. Nextcloud offers a modern, on premise content collaboration platform with real-time document editing, video chat & groupware on mobile, desktop and web. Sign up for a free Nextcloud account https://nextcloud.com/sign-up/
LinShare
True Open Source Secure File Sharing Solution We are committed to providing a reliable Open Source file-sharing solution, expertly designed to meet the highest standards of diverse industries, such as government and finance Try the Demo https://linshare.app/
Twake Drive
The open-source alternative to Google Drive. Privacy-First Open Source Workplace. Twake workplace open source business. Improve your effeciency with truly Open Source, all-in-one digital suite. Enhance the security in every aspect of your professional and private life. Sign up https://sign-up.twake.app/
SpaceDrive
One Explorer. All Your Files. Unify files from all your devices and clouds into a single, easy-to-use explorer. Designed for creators, hoarders and the painfully disorganized. Download desktop app (mobile coming soon) https://www.spacedrive.com/
ente
Safe Home for your photos Store, share, and discover your memories with end-to-end encryption. End-to-end encryption, durable storage and simple sharing. Packed with these and much more into our beautiful open source apps. Get started https://web.ente.io
fileStash
Turn your FTP server into... Filestash is the enterprise-grade file manager connecting your storage with your identity provider and authorisations. Try the demo https://demo.filestash.app
STORJ
Disruptively fast. Globally secure. S3-compatible distributed cloud services that make the most demanding workflows fast and affordable. Fast track your journey toward high performance cloud services. Storj pricing is consistent and competitive in meeting or exceeding your cloud services needs. Give the products a try to experience the benefits of the distributed cloud. Get Started https://www.storj.io/get-started
FireFile
The open‑source alternative to Dropbox. Firefiles lets you setup a cloud drive with the backend of your choice and lets you seamlessly manage your files across multiple providers. It revolutionizes cloud storage management by offering a unified platform for all your storage needs. Sign up Free https://beta.firefiles.app
originally posted at https://stacker.news/items/973626
-
 @ 57d1a264:69f1fee1
2025-05-06 06:00:25
@ 57d1a264:69f1fee1
2025-05-06 06:00:25Album art didn’t always exist. In the early 1900s, recorded music was still a novelty, overshadowed by sales of sheet music. Early vinyl records were vastly different from what we think of today: discs were sold individually and could only hold up to four minutes of music per side. Sometimes, only one side of the record was used. One of the most popular records of 1910, for example, was “Come, Josephine, in My Flying Machine”: it clocked in at two minutes and 39 seconds.
The invention of album art can get lost in the story of technological mastery. But among all the factors that contributed to the rise of recorded music, it stands as one of the few that was wholly driven by creators themselves. Album art — first as marketing material, then as pure creative expression — turned an audio-only medium into a multi-sensory experience.
This is the story of the people who made music visible.
originally posted at https://stacker.news/items/972642