-
 @ 21335073:a244b1ad
2025-05-21 16:58:36
@ 21335073:a244b1ad
2025-05-21 16:58:36The other day, I had the privilege of sitting down with one of my favorite living artists. Our conversation was so captivating that I felt compelled to share it. I’m leaving his name out for privacy.
Since our last meeting, I’d watched a documentary about his life, one he’d helped create. I told him how much I admired his openness in it. There’s something strange about knowing intimate details of someone’s life when they know so little about yours—it’s almost like I knew him too well for the kind of relationship we have.
He paused, then said quietly, with a shy grin, that watching the documentary made him realize how “odd and eccentric” he is. I laughed and told him he’s probably the sanest person I know. Because he’s lived fully, chasing love, passion, and purpose with hardly any regrets. He’s truly lived.
Today, I turn 44, and I’ll admit I’m a bit eccentric myself. I think I came into the world this way. I’ve made mistakes along the way, but I carry few regrets. Every misstep taught me something. And as I age, I’m not interested in blending in with the world—I’ll probably just lean further into my own brand of “weird.” I want to live life to the brim. The older I get, the more I see that the “normal” folks often seem less grounded than the eccentric artists who dare to live boldly. Life’s too short to just exist, actually live.
I’m not saying to be strange just for the sake of it. But I’ve seen what the crowd celebrates, and I’m not impressed. Forge your own path, even if it feels lonely or unpopular at times.
It’s easy to scroll through the news and feel discouraged. But actually, this is one of the most incredible times to be alive! I wake up every day grateful to be here, now. The future is bursting with possibility—I can feel it.
So, to my fellow weirdos on nostr: stay bold. Keep dreaming, keep pushing, no matter what’s trending. Stay wild enough to believe in a free internet for all. Freedom is radical—hold it tight. Live with the soul of an artist and the grit of a fighter. Thanks for inspiring me and so many others to keep hoping. Thank you all for making the last year of my life so special.
-
 @ 39cc53c9:27168656
2025-05-27 09:21:53
@ 39cc53c9:27168656
2025-05-27 09:21:53The new website is finally live! I put in a lot of hard work over the past months on it. I'm proud to say that it's out now and it looks pretty cool, at least to me!
Why rewrite it all?
The old kycnot.me site was built using Python with Flask about two years ago. Since then, I've gained a lot more experience with Golang and coding in general. Trying to update that old codebase, which had a lot of design flaws, would have been a bad idea. It would have been like building on an unstable foundation.
That's why I made the decision to rewrite the entire application. Initially, I chose to use SvelteKit with JavaScript. I did manage to create a stable site that looked similar to the new one, but it required Jav aScript to work. As I kept coding, I started feeling like I was repeating "the Python mistake". I was writing the app in a language I wasn't very familiar with (just like when I was learning Python at that mom ent), and I wasn't happy with the code. It felt like spaghetti code all the time.
So, I made a complete U-turn and started over, this time using Golang. While I'm not as proficient in Golang as I am in Python now, I find it to be a very enjoyable language to code with. Most aof my recent pr ojects have been written in Golang, and I'm getting the hang of it. I tried to make the best decisions I could and structure the code as well as possible. Of course, there's still room for improvement, which I'll address in future updates.
Now I have a more maintainable website that can scale much better. It uses a real database instead of a JSON file like the old site, and I can add many more features. Since I chose to go with Golang, I mad e the "tradeoff" of not using JavaScript at all, so all the rendering load falls on the server. But I believe it's a tradeoff that's worth it.
What's new
- UI/UX - I've designed a new logo and color palette for kycnot.me. I think it looks pretty cool and cypherpunk. I am not a graphic designer, but I think I did a decent work and I put a lot of thinking on it to make it pleasant!
- Point system - The new point system provides more detailed information about the listings, and can be expanded to cover additional features across all services. Anyone can request a new point!
- ToS Scrapper: I've implemented a powerful automated terms-of-service scrapper that collects all the ToS pages from the listings. It saves you from the hassle of reading the ToS by listing the lines that are suspiciously related to KYC/AML practices. This is still in development and it will improve for sure, but it works pretty fine right now!
- Search bar - The new search bar allows you to easily filter services. It performs a full-text search on the Title, Description, Category, and Tags of all the services. Looking for VPN services? Just search for "vpn"!
- Transparency - To be more transparent, all discussions about services now take place publicly on GitLab. I won't be answering any e-mails (an auto-reply will prompt to write to the corresponding Gitlab issue). This ensures that all service-related matters are publicly accessible and recorded. Additionally, there's a real-time audits page that displays database changes.
- Listing Requests - I have upgraded the request system. The new form allows you to directly request services or points without any extra steps. In the future, I plan to enable requests for specific changes to parts of the website.
- Lightweight and fast - The new site is lighter and faster than its predecessor!
- Tor and I2P - At last! kycnot.me is now officially on Tor and I2P!
How?
This rewrite has been a labor of love, in the end, I've been working on this for more than 3 months now. I don't have a team, so I work by myself on my free time, but I find great joy in helping people on their private journey with cryptocurrencies. Making it easier for individuals to use cryptocurrencies without KYC is a goal I am proud of!
If you appreciate my work, you can support me through the methods listed here. Alternatively, feel free to send me an email with a kind message!
Technical details
All the code is written in Golang, the website makes use of the chi router for the routing part. I also make use of BigCache for caching database requests. There is 0 JavaScript, so all the rendering load falls on the server, this means it needed to be efficient enough to not drawn with a few users since the old site was reporting about 2M requests per month on average (note that this are not unique users).
The database is running with mariadb, using gorm as the ORM. This is more than enough for this project. I started working with an
sqlitedatabase, but I ended up migrating to mariadb since it works better with JSON.The scraper is using chromedp combined with a series of keywords, regex and other logic. It runs every 24h and scraps all the services. You can find the scraper code here.
The frontend is written using Golang Templates for the HTML, and TailwindCSS plus DaisyUI for the CSS classes framework. I also use some plain CSS, but it's minimal.
The requests forms is the only part of the project that requires JavaScript to be enabled. It is needed for parsing some from fields that are a bit complex and for the "captcha", which is a simple Proof of Work that runs on your browser, destinated to avoid spam. For this, I use mCaptcha.
-
 @ 51bbb15e:b77a2290
2025-05-21 00:24:36
@ 51bbb15e:b77a2290
2025-05-21 00:24:36Yeah, I’m sure everything in the file is legit. 👍 Let’s review the guard witness testimony…Oh wait, they weren’t at their posts despite 24/7 survellience instructions after another Epstein “suicide” attempt two weeks earlier. Well, at least the video of the suicide is in the file? Oh wait, a techical glitch. Damn those coincidences!
At this point, the Trump administration has zero credibility with me on anything related to the Epstein case and his clients. I still suspect the administration is using the Epstein files as leverage to keep a lot of RINOs in line, whereas they’d be sabotaging his agenda at every turn otherwise. However, I just don’t believe in ends-justify-the-means thinking. It’s led almost all of DC to toss out every bit of the values they might once have had.
-
 @ 04c915da:3dfbecc9
2025-05-20 15:53:48
@ 04c915da:3dfbecc9
2025-05-20 15:53:48This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ 866e0139:6a9334e5
2025-05-27 10:15:17
@ 866e0139:6a9334e5
2025-05-27 10:15:17Autor: Milosz Matuschek. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie auch in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
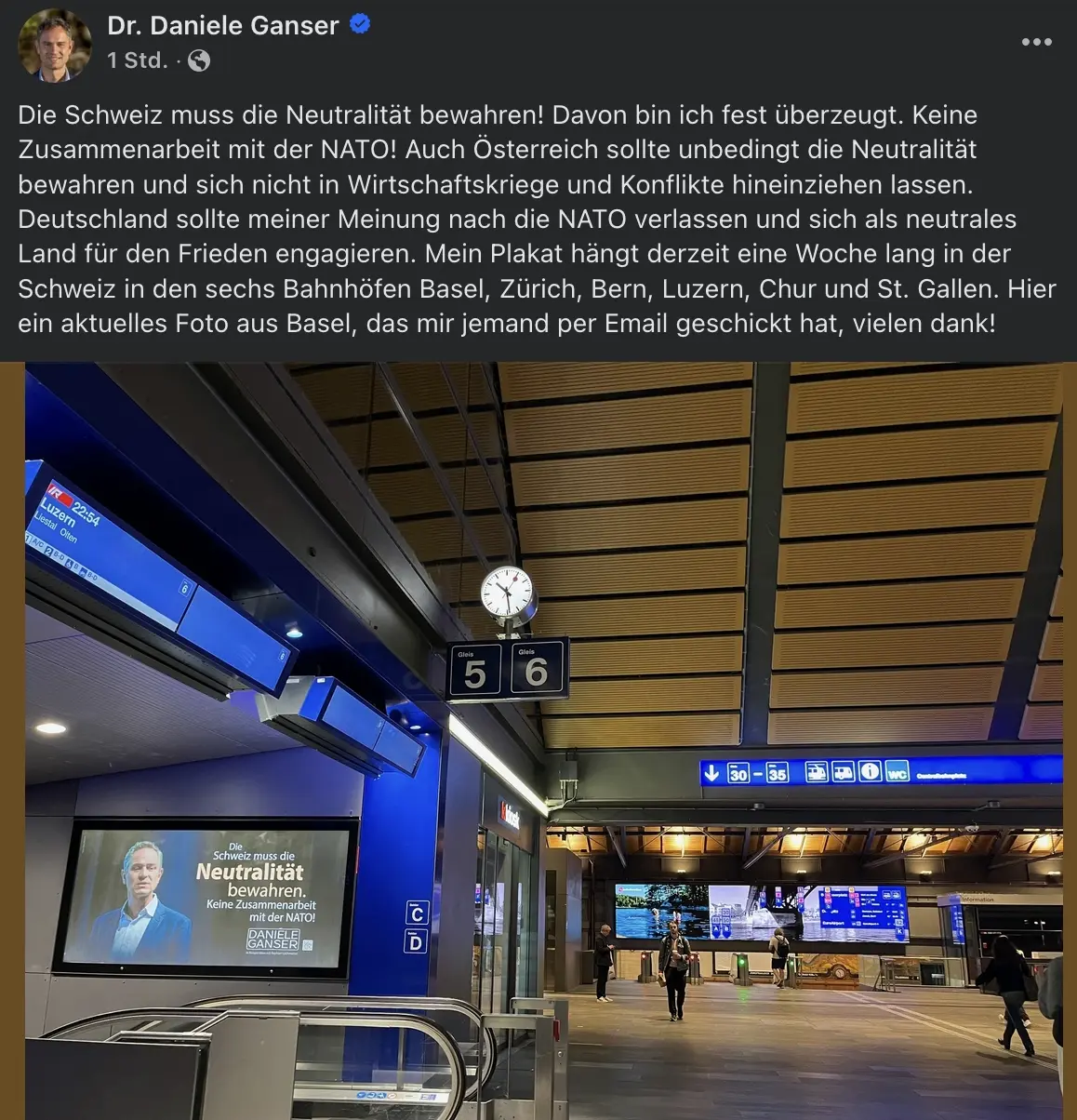
Der Schweizer Historiker Daniele Ganser startet eine Plakataktion. Auf Facebook schreibt er:
"Dieses Plakat habe ich ab heute an sechs Bahnhöfen in der Schweiz aufhängen lassen: Die Schweiz muss die Neutralität bewahren. Keine Zusammenarbeit mit der NATO!
Die Aktion läuft eine Woche. Das Plakat hängt in Basel (Gleis 5 und 7), Zürich (Gleis 9 und 12), Bern (Gleis 3 und 11), Luzern (Gleis 7 und 11), St. Gallen (Gleis 1 und 2) und Chur (Gleis 4 und Arosabahn).
Wenn jemand ein Plakat sieht und fotografiert und es mir per Email schickt freut mich das!
https://globalbridge.ch/die-schweiz-muss-die.../
Daniele Ganser kann man über folgende Seite kontaktieren.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 04c915da:3dfbecc9
2025-05-20 15:50:22
@ 04c915da:3dfbecc9
2025-05-20 15:50:22There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ 04c915da:3dfbecc9
2025-05-20 15:47:16
@ 04c915da:3dfbecc9
2025-05-20 15:47:16Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 6ad3e2a3:c90b7740
2025-05-20 13:49:50
@ 6ad3e2a3:c90b7740
2025-05-20 13:49:50I’ve written about MSTR twice already, https://www.chrisliss.com/p/mstr and https://www.chrisliss.com/p/mstr-part-2, but I want to focus on legendary short seller James Chanos’ current trade wherein he buys bitcoin (via ETF) and shorts MSTR, in essence to “be like Mike” Saylor who sells MSTR shares at the market and uses them to add bitcoin to the company’s balance sheet. After all, if it’s good enough for Saylor, why shouldn’t everyone be doing it — shorting a company whose stock price is more than 2x its bitcoin holdings and using the proceeds to buy the bitcoin itself?
Saylor himself has said selling shares at 2x NAV (net asset value) to buy bitcoin is like selling dollars for two dollars each, and Chanos has apparently decided to get in while the getting (market cap more than 2x net asset value) is good. If the price of bitcoin moons, sending MSTR’s shares up, you are more than hedged in that event, too. At least that’s the theory.
The problem with this bet against MSTR’s mNAV, i.e., you are betting MSTR’s market cap will converge 1:1 toward its NAV in the short and medium term is this trade does not exist in a vacuum. Saylor has described how his ATM’s (at the market) sales of shares are accretive in BTC per share because of this very premium they carry. Yes, we’ll dilute your shares of the company, but because we’re getting you 2x the bitcoin per share, you are getting an ever smaller slice of an ever bigger overall pie, and the pie is growing 2x faster than your slice is reducing. (I https://www.chrisliss.com/p/mstr how this works in my first post.)
But for this accretion to continue, there must be a constant supply of “greater fools” to pony up for the infinitely printable shares which contain only half their value in underlying bitcoin. Yes, those shares will continue to accrete more BTC per share, but only if there are more fools willing to make this trade in the future. So will there be a constant supply of such “fools” to keep fueling MSTR’s mNAV multiple indefinitely?
Yes, there will be in my opinion because you have to look at the trade from the prospective fools’ perspective. Those “fools” are not trading bitcoin for MSTR, they are trading their dollars, selling other equities to raise them maybe, but in the end it’s a dollars for shares trade. They are not selling bitcoin for them.
You might object that those same dollars could buy bitcoin instead, so they are surely trading the opportunity cost of buying bitcoin for them, but if only 5-10 percent of the market (or less) is buying bitcoin itself, the bucket in which which those “fools” reside is the entire non-bitcoin-buying equity market. (And this is not considering the even larger debt market which Saylor has yet to tap in earnest.)
So for those 90-95 percent who do not and are not presently planning to own bitcoin itself, is buying MSTR a fool’s errand, so to speak? Not remotely. If MSTR shares are infinitely printable ATM, they are still less so than the dollar and other fiat currencies. And MSTR shares are backed 2:1 by bitcoin itself, while the fiat currencies are backed by absolutely nothing. So if you hold dollars or euros, trading them for MSTR shares is an errand more sage than foolish.
That’s why this trade (buying BTC and shorting MSTR) is so dangerous. Not only are there many people who won’t buy BTC buying MSTR, there are many funds and other investment entities who are only able to buy MSTR.
Do you want to get BTC at 1:1 with the 5-10 percent or MSTR backed 2:1 with the 90-95 percent. This is a bit like medical tests that have a 95 percent accuracy rate for an asymptomatic disease that only one percent of the population has. If someone tests positive, it’s more likely to be a false one than an indication he has the disease*. The accuracy rate, even at 19:1, is subservient to the size of the respective populations.
At some point this will no longer be the case, but so long as the understanding of bitcoin is not widespread, so long as the dollar is still the unit of account, the “greater fools” buying MSTR are still miles ahead of the greatest fools buying neither, and the stock price and mNAV should only increase.
. . .
One other thought: it’s more work to play defense than offense because the person on offense knows where he’s going, and the defender can only react to him once he moves. Similarly, Saylor by virtue of being the issuer of the shares knows when more will come online while Chanos and other short sellers are borrowing them to sell in reaction to Saylor’s strategy. At any given moment, Saylor can pause anytime, choosing to issue convertible debt or preferred shares with which to buy more bitcoin, and the shorts will not be given advance notice.
If the price runs, and there is no ATM that week because Saylor has stopped on a dime, so to speak, the shorts will be left having to scramble to change directions and buy the shares back to cover. Their momentum might be in the wrong direction, though, and like Allen Iverson breaking ankles with a crossover, Saylor might trigger a massive short squeeze, rocketing the share price ever higher. That’s why he actually welcomes Chanos et al trying this copycat strategy — it becomes the fuel for outsized gains.
For that reason, news that Chanos is shorting MSTR has not shaken my conviction, though there are other more pertinent https://www.chrisliss.com/p/mstr-part-2 with MSTR, of which one should be aware. And as always, do your own due diligence before investing in anything.
* To understand this, consider a population of 100,000, with one percent having a disease. That means 1,000 have it, 99,000 do not. If the test is 95 percent accurate, and everyone is tested, 950 of the 1,000 will test positive (true positives), 50 who have it will test negative (false negatives.) Of the positives, 95 percent of 99,000 (94,050) will test negative (true negatives) and five percent (4,950) will test positive (false positives). That means 4,950 out of 5,900 positives (84%) will be false.
-
 @ 39cc53c9:27168656
2025-05-27 09:21:51
@ 39cc53c9:27168656
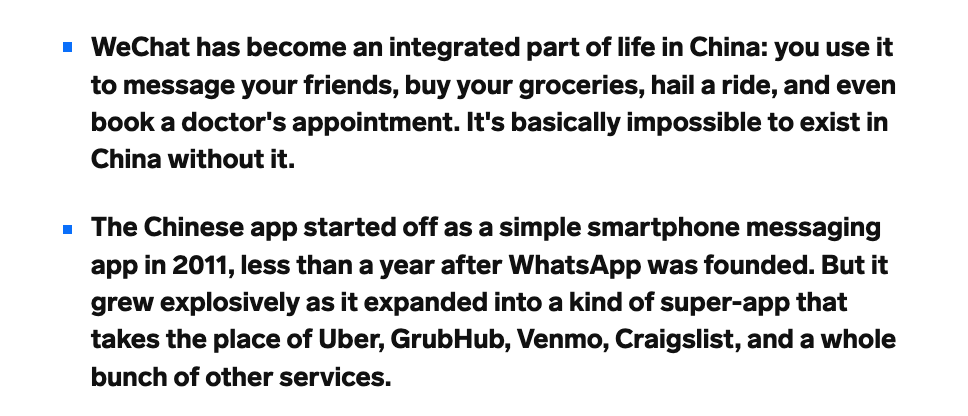
2025-05-27 09:21:51Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations.
Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms.
Rights for Illusions
KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks?
The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors."
However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% ^1 – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service.
Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy.
To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% ^1 of less-than-careful criminals.
KYC? Not you.
KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. ^2
KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible.
For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded.
Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether.
It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms.
You're not welcome
Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right?
This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to.
Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely.
Your identity has been stolen
KYC data has been found to be for sale on many dark net markets^3. Exchanges may have leaks or hacks, and such leaks contain very sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it?
As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. ^3
In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised.
(they) Know Your Coins
You may already know that Bitcoin and most cryptocurrencies have a transparent public blockchain, meaning that all data is shown unencrypted for everyone to see and recorded forever. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced.
If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with.
Conclusions
To sum up, KYC does not protect individuals; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred.
The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies.
The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable.
Edited 20/03/2024 * Add reference to the 1% statement on Rights for Illusions section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity ^1
-
 @ 39cc53c9:27168656
2025-05-27 09:21:50
@ 39cc53c9:27168656
2025-05-27 09:21:50Over the past few months, I've dedicated my time to a complete rewrite of the kycnot.me website. The technology stack remains unchanged; Golang paired with TailwindCSS. However, I've made some design choices in this iteration that I believe significantly enhance the site. Particularly to backend code.
UI Improvements
You'll notice a refreshed UI that retains the original concept but has some notable enhancements. The service list view is now more visually engaging, it displays additional information in a more aesthetically pleasing manner. Both filtering and searching functionalities have been optimized for speed and user experience.
Service pages have been also redesigned to highlight key information at the top, with the KYC Level box always accessible. The display of service attributes is now more visually intuitive.
The request form, especially the Captcha, has undergone substantial improvements. The new self-made Captcha is robust, addressing the reliability issues encountered with the previous version.
Terms of Service Summarizer
A significant upgrade is the Terms of Service summarizer/reviewer, now powered by AI (GPT-4-turbo). It efficiently condenses each service's ToS, extracting and presenting critical points, including any warnings. Summaries are updated monthly, processing over 40 ToS pages via the OpenAI API using a self-crafted and thoroughly tested prompt.
Nostr Comments
I've integrated a comment section for each service using Nostr. For guidance on using this feature, visit the dedicated how-to page.
Database
The backend database has transitioned to pocketbase, an open-source Golang backend that has been a pleasure to work with. I maintain an updated fork of the Golang SDK for pocketbase at pluja/pocketbase.
Scoring
The scoring algorithm has also been refined to be more fair. Despite I had considered its removal due to the complexity it adds (it is very difficult to design a fair scoring system), some users highlighted its value, so I kept it. The updated algorithm is available open source.
Listings
Each listing has been re-evaluated, and the ones that were no longer operational were removed. New additions are included, and the backlog of pending services will be addressed progressively, since I still have access to the old database.
API
The API now offers more comprehensive data. For more details, check here.
About Page
The About page has been restructured for brevity and clarity.
Other Changes
Extensive changes have been implemented in the server-side logic, since the whole code base was re-written from the ground up. I may discuss these in a future post, but for now, I consider the current version to be just a bit beyond beta, and additional updates are planned in the coming weeks.
-
 @ 39cc53c9:27168656
2025-05-27 09:21:48
@ 39cc53c9:27168656
2025-05-27 09:21:48I'm launching a new service review section on this blog in collaboration with OrangeFren. These reviews are sponsored, yet the sponsorship does not influence the outcome of the evaluations. Reviews are done in advance, then, the service provider has the discretion to approve publication without modifications.
Sponsored reviews are independent from the kycnot.me list, being only part of the blog. The reviews have no impact on the scores of the listings or their continued presence on the list. Should any issues arise, I will not hesitate to remove any listing.
The review
WizardSwap is an instant exchange centred around privacy coins. It was launched in 2020 making it old enough to have weathered the 2021 bull run and the subsequent bearish year.
| Pros | Cons | |------|------| | Tor-friendly | Limited liquidity | | Guarantee of no KYC | Overly simplistic design | | Earn by providing liquidity | |
Rating: ★★★★★ Service Website: wizardswap.io
Liquidity
Right off the bat, we'll start off by pointing out that WizardSwap relies on its own liquidity reserves, meaning they aren't just a reseller of Binance or another exchange. They're also committed to a no-KYC policy, when asking them, they even promised they would rather refund a user their original coins, than force them to undergo any sort of verification.
On the one hand, full control over all their infrastructure gives users the most privacy and conviction about the KYC policies remaining in place.
On the other hand, this means the liquidity available for swapping isn't huge. At the time of testing we could only purchase at most about 0.73 BTC with XMR.
It's clear the team behind WizardSwap is aware of this shortfall and so they've come up with a solution unique among instant exchanges. They let you, the user, deposit any of the currencies they support into your account and earn a profit on the trades made using your liquidity.
Trading
Fees on WizardSwap are middle-of-the-pack. The normal fee is 2.2%. That's more than some exchanges that reserve the right to suddenly demand you undergo verification, yet less than half the fees on some other privacy-first exchanges. However as we mentioned in the section above you can earn almost all of that fee (2%) if you provide liquidity to WizardSwap.
It's good that with the current Bitcoin fee market their fees are constant regardless of how much, or how little, you send. This is in stark contrast with some of the alternative swap providers that will charge you a massive premium when attempting to swap small amounts of BTC away.
Test trades
Test trades are always performed without previous notice to the service provider.
During our testing we performed a few test trades and found that every single time WizardSwap immediately detected the incoming transaction and the amount we received was exactly what was quoted before depositing. The fees were inline with what WizardSwap advertises.

- Monero payment proof
- Bitcoin received
- Wizardswap TX link - it's possible that this link may cease to be valid at some point in the future.
ToS and KYC
WizardSwap does not have a Terms of Service or a Privacy Policy page, at least none that can be found by users. Instead, they offer a FAQ section where they addresses some basic questions.
The site does not mention any KYC or AML practices. It also does not specify how refunds are handled in case of failure. However, based on the FAQ section "What if I send funds after the offer expires?" it can be inferred that contacting support is necessary and network fees will be deducted from any refund.
UI & Tor
WizardSwap can be visited both via your usual browser and Tor Browser. Should you decide on the latter you'll find that the website works even with the most strict settings available in the Tor Browser (meaning no JavaScript).
However, when disabling Javascript you'll miss the live support chat, as well as automatic refreshing of the trade page. The lack of the first means that you will have no way to contact support from the trade page if anything goes wrong during your swap, although you can do so by mail.
One important thing to have in mind is that if you were to accidentally close the browser during the swap, and you did not save the swap ID or your browser history is disabled, you'll have no easy way to return to the trade. For this reason we suggest when you begin a trade to copy the url or ID to someplace safe, before sending any coins to WizardSwap.
The UI you'll be greeted by is simple, minimalist, and easy to navigate. It works well not just across browsers, but also across devices. You won't have any issues using this exchange on your phone.
Getting in touch
The team behind WizardSwap appears to be most active on X (formerly Twitter): https://twitter.com/WizardSwap_io
If you have any comments or suggestions about the exchange make sure to reach out to them. In the past they've been very receptive to user feedback, for instance a few months back WizardSwap was planning on removing DeepOnion, but the community behind that project got together ^1 and after reaching out WizardSwap reversed their decision ^2.
You can also contact them via email at:
support @ wizardswap . ioDisclaimer
None of the above should be understood as investment or financial advice. The views are our own only and constitute a faithful representation of our experience in using and investigating this exchange. This review is not a guarantee of any kind on the services rendered by the exchange. Do your own research before using any service.
-
 @ 39cc53c9:27168656
2025-05-27 09:21:46
@ 39cc53c9:27168656
2025-05-27 09:21:46Bitcoin enthusiasts frequently and correctly remark how much value it adds to Bitcoin not to have a face, a leader, or a central authority behind it. This particularity means there isn't a single person to exert control over, or a single human point of failure who could become corrupt or harmful to the project.
Because of this, it is said that no other coin can be equally valuable as Bitcoin in terms of decentralization and trustworthiness. Bitcoin is unique not just for being first, but also because of how the events behind its inception developed. This implies that, from Bitcoin onwards, any coin created would have been created by someone, consequently having an authority behind it. For this and some other reasons, some people refer to Bitcoin as "The Immaculate Conception".
While other coins may have their own unique features and advantages, they may not be able to replicate Bitcoin's community-driven nature. However, one other cryptocurrency shares a similar story of mystery behind its creation: Monero.
History of Monero
Bytecoin and CryptoNote
In March 2014, a Bitcointalk thread titled "Bytecoin. Secure, private, untraceable since 2012" was initiated by a user under the nickname "DStrange"^1^. DStrange presented Bytecoin (BCN) as a unique cryptocurrency, in operation since July 2012. Unlike Bitcoin, it employed a new algorithm known as CryptoNote.
DStrange apparently stumbled upon the Bytecoin website by chance while mining a dying bitcoin fork, and decided to create a thread on Bitcointalk^1^. This sparked curiosity among some users, who wondered how could Bytecoin remain unnoticed since its alleged launch in 2012 until then^2^.
Some time after, a user brought up the "CryptoNote v2.0" whitepaper for the first time, underlining its innovative features^4^. Authored by the pseudonymous Nicolas van Saberhagen in October 2013, the CryptoNote v2 whitepaper^5^ highlighted the traceability and privacy problems in Bitcoin. Saberhagen argued that these flaws could not be quickly fixed, suggesting it would be more efficient to start a new project rather than trying to patch the original^5^, an statement simmilar to the one from Satoshi Nakamoto^6^.
Checking with Saberhagen's digital signature, the release date of the whitepaper seemed correct, which would mean that Cryptonote (v1) was created in 2012^7^, although there's an important detail: "Signing time is from the clock on the signer's computer" ^9^.
Moreover, the whitepaper v1 contains a footnote link to a Bitcointalk post dated May 5, 2013^10^, making it impossible for the whitepaper to have been signed and released on December 12, 2012.
As the narrative developed, users discovered that a significant 80% portion of Bytecoin had been pre-mined^11^ and blockchain dates seemed to be faked to make it look like it had been operating since 2012, leading to controversy surrounding the project.
The origins of CryptoNote and Bytecoin remain mysterious, leaving suspicions of a possible scam attempt, although the whitepaper had a good amount of work and thought on it.
The fork
In April 2014, the Bitcointalk user
thankful_for_today, who had also participated in the Bytecoin thread^12^, announced plans to launch a Bytecoin fork named Bitmonero^13^.The primary motivation behind this fork was "Because there is a number of technical and marketing issues I wanted to do differently. And also because I like ideas and technology and I want it to succeed"^14^. This time Bitmonero did things different from Bytecoin: there was no premine or instamine, and no portion of the block reward went to development.
However, thankful_for_today proposed controversial changes that the community disagreed with. Johnny Mnemonic relates the events surrounding Bitmonero and thankful_for_today in a Bitcointalk comment^15^:
When thankful_for_today launched BitMonero [...] he ignored everything that was discussed and just did what he wanted. The block reward was considerably steeper than what everyone was expecting. He also moved forward with 1-minute block times despite everyone's concerns about the increase of orphan blocks. He also didn't address the tail emission concern that should've (in my opinion) been in the code at launch time. Basically, he messed everything up. Then, he disappeared.
After disappearing for a while, thankful_for_today returned to find that the community had taken over the project. Johnny Mnemonic continues:
I, and others, started working on new forks that were closer to what everyone else was hoping for. [...] it was decided that the BitMonero project should just be taken over. There were like 9 or 10 interested parties at the time if my memory is correct. We voted on IRC to drop the "bit" from BitMonero and move forward with the project. Thankful_for_today suddenly resurfaced, and wasn't happy to learn the community had assumed control of the coin. He attempted to maintain his own fork (still calling it "BitMonero") for a while, but that quickly fell into obscurity.
The unfolding of these events show us the roots of Monero. Much like Satoshi Nakamoto, the creators behind CryptoNote/Bytecoin and thankful_for_today remain a mystery^17^, having disappeared without a trace. This enigma only adds to Monero's value.
Since community took over development, believing in the project's potential and its ability to be guided in a better direction, Monero was given one of Bitcoin's most important qualities: a leaderless nature. With no single face or entity directing its path, Monero is safe from potential corruption or harm from a "central authority".
The community continued developing Monero until today. Since then, Monero has undergone a lot of technological improvements, migrations and achievements such as RingCT and RandomX. It also has developed its own Community Crowdfundinc System, conferences such as MoneroKon and Monerotopia are taking place every year, and has a very active community around it.
Monero continues to develop with goals of privacy and security first, ease of use and efficiency second. ^16^
This stands as a testament to the power of a dedicated community operating without a central figure of authority. This decentralized approach aligns with the original ethos of cryptocurrency, making Monero a prime example of community-driven innovation. For this, I thank all the people involved in Monero, that lead it to where it is today.
If you find any information that seems incorrect, unclear or any missing important events, please contact me and I will make the necessary changes.
Sources of interest
- https://forum.getmonero.org/20/general-discussion/211/history-of-monero
- https://monero.stackexchange.com/questions/852/what-is-the-origin-of-monero-and-its-relationship-to-bytecoin
- https://en.wikipedia.org/wiki/Monero
- https://bitcointalk.org/index.php?topic=583449.0
- https://bitcointalk.org/index.php?topic=563821.0
- https://bitcointalk.org/index.php?action=profile;u=233561
- https://bitcointalk.org/index.php?topic=512747.0
- https://bitcointalk.org/index.php?topic=740112.0
- https://monero.stackexchange.com/a/1024
- https://inspec2t-project.eu/cryptocurrency-with-a-focus-on-anonymity-these-facts-are-known-about-monero/
- https://medium.com/coin-story/coin-perspective-13-riccardo-spagni-69ef82907bd1
- https://www.getmonero.org/resources/about/
- https://www.wired.com/2017/01/monero-drug-dealers-cryptocurrency-choice-fire/
- https://www.monero.how/why-monero-vs-bitcoin
- https://old.reddit.com/r/Monero/comments/u8e5yr/satoshi_nakamoto_talked_about_privacy_features/
-
 @ 4ba8e86d:89d32de4
2025-05-19 22:33:46
@ 4ba8e86d:89d32de4
2025-05-19 22:33:46O que é Cwtch? Cwtch (/kʊtʃ/ - uma palavra galesa que pode ser traduzida aproximadamente como “um abraço que cria um lugar seguro”) é um protocolo de mensagens multipartidário descentralizado, que preserva a privacidade, que pode ser usado para construir aplicativos resistentes a metadados.
Como posso pronunciar Cwtch? Como "kutch", para rimar com "butch".
Descentralizado e Aberto : Não existe “serviço Cwtch” ou “rede Cwtch”. Os participantes do Cwtch podem hospedar seus próprios espaços seguros ou emprestar sua infraestrutura para outras pessoas que buscam um espaço seguro. O protocolo Cwtch é aberto e qualquer pessoa é livre para criar bots, serviços e interfaces de usuário e integrar e interagir com o Cwtch.
Preservação de privacidade : toda a comunicação no Cwtch é criptografada de ponta a ponta e ocorre nos serviços cebola Tor v3.
Resistente a metadados : O Cwtch foi projetado de forma que nenhuma informação seja trocada ou disponibilizada a ninguém sem seu consentimento explícito, incluindo mensagens durante a transmissão e metadados de protocolo
Uma breve história do bate-papo resistente a metadados Nos últimos anos, a conscientização pública sobre a necessidade e os benefícios das soluções criptografadas de ponta a ponta aumentou com aplicativos como Signal , Whatsapp e Wire. que agora fornecem aos usuários comunicações seguras.
No entanto, essas ferramentas exigem vários níveis de exposição de metadados para funcionar, e muitos desses metadados podem ser usados para obter detalhes sobre como e por que uma pessoa está usando uma ferramenta para se comunicar.
Uma ferramenta que buscou reduzir metadados é o Ricochet lançado pela primeira vez em 2014. Ricochet usou os serviços cebola Tor v2 para fornecer comunicação criptografada segura de ponta a ponta e para proteger os metadados das comunicações.
Não havia servidores centralizados que auxiliassem no roteamento das conversas do Ricochet. Ninguém além das partes envolvidas em uma conversa poderia saber que tal conversa está ocorrendo.
Ricochet tinha limitações; não havia suporte para vários dispositivos, nem existe um mecanismo para suportar a comunicação em grupo ou para um usuário enviar mensagens enquanto um contato está offline.
Isto tornou a adoção do Ricochet uma proposta difícil; mesmo aqueles em ambientes que seriam melhor atendidos pela resistência aos metadados, sem saber que ela existe.
Além disso, qualquer solução para comunicação descentralizada e resistente a metadados enfrenta problemas fundamentais quando se trata de eficiência, privacidade e segurança de grupo conforme definido pelo consenso e consistência da transcrição.
Alternativas modernas ao Ricochet incluem Briar , Zbay e Ricochet Refresh - cada ferramenta procura otimizar para um conjunto diferente de compensações, por exemplo, Briar procura permitir que as pessoas se comuniquem mesmo quando a infraestrutura de rede subjacente está inoperante, ao mesmo tempo que fornece resistência à vigilância de metadados.
O projeto Cwtch começou em 2017 como um protocolo de extensão para Ricochet, fornecendo conversas em grupo por meio de servidores não confiáveis, com o objetivo de permitir aplicativos descentralizados e resistentes a metadados como listas compartilhadas e quadros de avisos.
Uma versão alfa do Cwtch foi lançada em fevereiro de 2019 e, desde então, a equipe do Cwtch dirigida pela OPEN PRIVACY RESEARCH SOCIETY conduziu pesquisa e desenvolvimento em cwtch e nos protocolos, bibliotecas e espaços de problemas subjacentes.
Modelo de Risco.
Sabe-se que os metadados de comunicações são explorados por vários adversários para minar a segurança dos sistemas, para rastrear vítimas e para realizar análises de redes sociais em grande escala para alimentar a vigilância em massa. As ferramentas resistentes a metadados estão em sua infância e faltam pesquisas sobre a construção e a experiência do usuário de tais ferramentas.
https://nostrcheck.me/media/public/nostrcheck.me_9475702740746681051707662826.webp
O Cwtch foi originalmente concebido como uma extensão do protocolo Ricochet resistente a metadados para suportar comunicações assíncronas de grupos multiponto por meio do uso de infraestrutura anônima, descartável e não confiável.
Desde então, o Cwtch evoluiu para um protocolo próprio. Esta seção descreverá os vários riscos conhecidos que o Cwtch tenta mitigar e será fortemente referenciado no restante do documento ao discutir os vários subcomponentes da Arquitetura Cwtch.
Modelo de ameaça.
É importante identificar e compreender que os metadados são omnipresentes nos protocolos de comunicação; é de facto necessário que tais protocolos funcionem de forma eficiente e em escala. No entanto, as informações que são úteis para facilitar peers e servidores também são altamente relevantes para adversários que desejam explorar tais informações.
Para a definição do nosso problema, assumiremos que o conteúdo de uma comunicação é criptografado de tal forma que um adversário é praticamente incapaz de quebrá-lo veja tapir e cwtch para detalhes sobre a criptografia que usamos, e como tal nos concentraremos em o contexto para os metadados de comunicação.
Procuramos proteger os seguintes contextos de comunicação:
• Quem está envolvido em uma comunicação? Pode ser possível identificar pessoas ou simplesmente identificadores de dispositivos ou redes. Por exemplo, “esta comunicação envolve Alice, uma jornalista, e Bob, um funcionário público”.
• Onde estão os participantes da conversa? Por exemplo, “durante esta comunicação, Alice estava na França e Bob estava no Canadá”.
• Quando ocorreu uma conversa? O momento e a duração da comunicação podem revelar muito sobre a natureza de uma chamada, por exemplo, “Bob, um funcionário público, conversou com Alice ao telefone por uma hora ontem à noite. Esta é a primeira vez que eles se comunicam.” *Como a conversa foi mediada? O fato de uma conversa ter ocorrido por meio de um e-mail criptografado ou não criptografado pode fornecer informações úteis. Por exemplo, “Alice enviou um e-mail criptografado para Bob ontem, enquanto eles normalmente enviam apenas e-mails de texto simples um para o outro”.
• Sobre o que é a conversa? Mesmo que o conteúdo da comunicação seja criptografado, às vezes é possível derivar um contexto provável de uma conversa sem saber exatamente o que é dito, por exemplo, “uma pessoa ligou para uma pizzaria na hora do jantar” ou “alguém ligou para um número conhecido de linha direta de suicídio na hora do jantar”. 3 horas da manhã."
Além das conversas individuais, também procuramos defender-nos contra ataques de correlação de contexto, através dos quais múltiplas conversas são analisadas para obter informações de nível superior:
• Relacionamentos: Descobrir relações sociais entre um par de entidades analisando a frequência e a duração de suas comunicações durante um período de tempo. Por exemplo, Carol e Eve ligam uma para a outra todos os dias durante várias horas seguidas.
• Cliques: Descobrir relações sociais entre um grupo de entidades que interagem entre si. Por exemplo, Alice, Bob e Eva se comunicam entre si.
• Grupos vagamente conectados e indivíduos-ponte: descobrir grupos que se comunicam entre si através de intermediários, analisando cadeias de comunicação (por exemplo, toda vez que Alice fala com Bob, ela fala com Carol quase imediatamente depois; Bob e Carol nunca se comunicam).
• Padrão de Vida: Descobrir quais comunicações são cíclicas e previsíveis. Por exemplo, Alice liga para Eve toda segunda-feira à noite por cerca de uma hora. Ataques Ativos
Ataques de deturpação.
O Cwtch não fornece registro global de nomes de exibição e, como tal, as pessoas que usam o Cwtch são mais vulneráveis a ataques baseados em declarações falsas, ou seja, pessoas que fingem ser outras pessoas:
O fluxo básico de um desses ataques é o seguinte, embora também existam outros fluxos:
•Alice tem um amigo chamado Bob e outro chamado Eve
• Eve descobre que Alice tem um amigo chamado Bob
• Eve cria milhares de novas contas para encontrar uma que tenha uma imagem/chave pública semelhante à de Bob (não será idêntica, mas pode enganar alguém por alguns minutos)
• Eve chama essa nova conta de "Eve New Account" e adiciona Alice como amiga.
• Eve então muda seu nome em "Eve New Account" para "Bob"
• Alice envia mensagens destinadas a "Bob" para a conta falsa de Bob de Eve Como os ataques de declarações falsas são inerentemente uma questão de confiança e verificação, a única maneira absoluta de evitá-los é os usuários validarem absolutamente a chave pública. Obviamente, isso não é o ideal e, em muitos casos, simplesmente não acontecerá .
Como tal, pretendemos fornecer algumas dicas de experiência do usuário na interface do usuário para orientar as pessoas na tomada de decisões sobre confiar em contas e/ou distinguir contas que possam estar tentando se representar como outros usuários.
Uma nota sobre ataques físicos A Cwtch não considera ataques que exijam acesso físico (ou equivalente) à máquina do usuário como praticamente defensáveis. No entanto, no interesse de uma boa engenharia de segurança, ao longo deste documento ainda nos referiremos a ataques ou condições que exigem tal privilégio e indicaremos onde quaisquer mitigações que implementámos falharão.
Um perfil Cwtch.
Os usuários podem criar um ou mais perfis Cwtch. Cada perfil gera um par de chaves ed25519 aleatório compatível com Tor.
Além do material criptográfico, um perfil também contém uma lista de Contatos (outras chaves públicas do perfil Cwtch + dados associados sobre esse perfil, como apelido e (opcionalmente) mensagens históricas), uma lista de Grupos (contendo o material criptográfico do grupo, além de outros dados associados, como apelido do grupo e mensagens históricas).
Conversões entre duas partes: ponto a ponto
https://nostrcheck.me/media/public/nostrcheck.me_2186338207587396891707662879.webp
Para que duas partes participem de uma conversa ponto a ponto, ambas devem estar on-line, mas apenas uma precisa estar acessível por meio do serviço Onion. Por uma questão de clareza, muitas vezes rotulamos uma parte como “ponto de entrada” (aquele que hospeda o serviço cebola) e a outra parte como “ponto de saída” (aquele que se conecta ao serviço cebola).
Após a conexão, ambas as partes adotam um protocolo de autenticação que:
• Afirma que cada parte tem acesso à chave privada associada à sua identidade pública.
• Gera uma chave de sessão efêmera usada para criptografar todas as comunicações futuras durante a sessão.
Esta troca (documentada com mais detalhes no protocolo de autenticação ) é negável offline , ou seja, é possível para qualquer parte falsificar transcrições desta troca de protocolo após o fato e, como tal - após o fato - é impossível provar definitivamente que a troca aconteceu de forma alguma.
Após o protocolo de autenticação, as duas partes podem trocar mensagens livremente.
Conversas em Grupo e Comunicação Ponto a Servidor
Ao iniciar uma conversa em grupo, é gerada uma chave aleatória para o grupo, conhecida como Group Key. Todas as comunicações do grupo são criptografadas usando esta chave. Além disso, o criador do grupo escolhe um servidor Cwtch para hospedar o grupo. Um convite é gerado, incluindo o Group Key, o servidor do grupo e a chave do grupo, para ser enviado aos potenciais membros.
Para enviar uma mensagem ao grupo, um perfil se conecta ao servidor do grupo e criptografa a mensagem usando a Group Key, gerando também uma assinatura sobre o Group ID, o servidor do grupo e a mensagem. Para receber mensagens do grupo, um perfil se conecta ao servidor e baixa as mensagens, tentando descriptografá-las usando a Group Key e verificando a assinatura.
Detalhamento do Ecossistema de Componentes
O Cwtch é composto por várias bibliotecas de componentes menores, cada uma desempenhando um papel específico. Algumas dessas bibliotecas incluem:
- abertoprivacidade/conectividade: Abstração de rede ACN, atualmente suportando apenas Tor.
- cwtch.im/tapir: Biblioteca para construção de aplicativos p2p em sistemas de comunicação anônimos.
- cwtch.im/cwtch: Biblioteca principal para implementação do protocolo/sistema Cwtch.
- cwtch.im/libcwtch-go: Fornece ligações C para Cwtch para uso em implementações de UI.
TAPIR: Uma Visão Detalhada
Projetado para substituir os antigos canais de ricochete baseados em protobuf, o Tapir fornece uma estrutura para a construção de aplicativos anônimos.
Está dividido em várias camadas:
• Identidade - Um par de chaves ed25519, necessário para estabelecer um serviço cebola Tor v3 e usado para manter uma identidade criptográfica consistente para um par.
• Conexões – O protocolo de rede bruto que conecta dois pares. Até agora, as conexões são definidas apenas através do Tor v3 Onion Services.
• Aplicativos - As diversas lógicas que permitem um determinado fluxo de informações em uma conexão. Os exemplos incluem transcrições criptográficas compartilhadas, autenticação, proteção contra spam e serviços baseados em tokens. Os aplicativos fornecem recursos que podem ser referenciados por outros aplicativos para determinar se um determinado peer tem a capacidade de usar um determinado aplicativo hospedado.
• Pilhas de aplicativos - Um mecanismo para conectar mais de um aplicativo, por exemplo, a autenticação depende de uma transcrição criptográfica compartilhada e o aplicativo peer cwtch principal é baseado no aplicativo de autenticação.
Identidade.
Um par de chaves ed25519, necessário para estabelecer um serviço cebola Tor v3 e usado para manter uma identidade criptográfica consistente para um peer.
InitializeIdentity - de um par de chaves conhecido e persistente:i,I
InitializeEphemeralIdentity - de um par de chaves aleatório: ie,Ie
Aplicativos de transcrição.
Inicializa uma transcrição criptográfica baseada em Merlin que pode ser usada como base de protocolos baseados em compromisso de nível superior
O aplicativo de transcrição entrará em pânico se um aplicativo tentar substituir uma transcrição existente por uma nova (aplicando a regra de que uma sessão é baseada em uma e apenas uma transcrição).
Merlin é uma construção de transcrição baseada em STROBE para provas de conhecimento zero. Ele automatiza a transformação Fiat-Shamir, para que, usando Merlin, protocolos não interativos possam ser implementados como se fossem interativos.
Isto é significativamente mais fácil e menos sujeito a erros do que realizar a transformação manualmente e, além disso, também fornece suporte natural para:
• protocolos multi-round com fases alternadas de commit e desafio;
• separação natural de domínios, garantindo que os desafios estejam vinculados às afirmações a serem provadas;
• enquadramento automático de mensagens, evitando codificação ambígua de dados de compromisso;
• e composição do protocolo, usando uma transcrição comum para vários protocolos.
Finalmente, o Merlin também fornece um gerador de números aleatórios baseado em transcrição como defesa profunda contra ataques de entropia ruim (como reutilização de nonce ou preconceito em muitas provas). Este RNG fornece aleatoriedade sintética derivada de toda a transcrição pública, bem como dos dados da testemunha do provador e uma entrada auxiliar de um RNG externo.
Conectividade Cwtch faz uso do Tor Onion Services (v3) para todas as comunicações entre nós.
Fornecemos o pacote openprivacy/connectivity para gerenciar o daemon Tor e configurar e desmontar serviços cebola através do Tor.
Criptografia e armazenamento de perfil.
Os perfis são armazenados localmente no disco e criptografados usando uma chave derivada de uma senha conhecida pelo usuário (via pbkdf2).
Observe que, uma vez criptografado e armazenado em disco, a única maneira de recuperar um perfil é recuperando a senha - como tal, não é possível fornecer uma lista completa de perfis aos quais um usuário pode ter acesso até inserir uma senha.
Perfis não criptografados e a senha padrão Para lidar com perfis "não criptografados" (ou seja, que não exigem senha para serem abertos), atualmente criamos um perfil com uma senha codificada de fato .
Isso não é o ideal, preferiríamos confiar no material de chave fornecido pelo sistema operacional, de modo que o perfil fosse vinculado a um dispositivo específico, mas esses recursos são atualmente uma colcha de retalhos - também notamos, ao criar um perfil não criptografado, pessoas que usam Cwtch estão explicitamente optando pelo risco de que alguém com acesso ao sistema de arquivos possa descriptografar seu perfil.
Vulnerabilidades Relacionadas a Imagens e Entrada de Dados
Imagens Maliciosas
O Cwtch enfrenta desafios na renderização de imagens, com o Flutter utilizando Skia, embora o código subjacente não seja totalmente seguro para a memória.
Realizamos testes de fuzzing nos componentes Cwtch e encontramos um bug de travamento causado por um arquivo GIF malformado, levando a falhas no kernel. Para mitigar isso, adotamos a política de sempre habilitar cacheWidth e/ou cacheHeight máximo para widgets de imagem.
Identificamos o risco de imagens maliciosas serem renderizadas de forma diferente em diferentes plataformas, como evidenciado por um bug no analisador PNG da Apple.
Riscos de Entrada de Dados
Um risco significativo é a interceptação de conteúdo ou metadados por meio de um Input Method Editor (IME) em dispositivos móveis. Mesmo aplicativos IME padrão podem expor dados por meio de sincronização na nuvem, tradução online ou dicionários pessoais.
Implementamos medidas de mitigação, como enableIMEPersonalizedLearning: false no Cwtch 1.2, mas a solução completa requer ações em nível de sistema operacional e é um desafio contínuo para a segurança móvel.
Servidor Cwtch.
O objetivo do protocolo Cwtch é permitir a comunicação em grupo através de infraestrutura não confiável .
Ao contrário dos esquemas baseados em retransmissão, onde os grupos atribuem um líder, um conjunto de líderes ou um servidor confiável de terceiros para garantir que cada membro do grupo possa enviar e receber mensagens em tempo hábil (mesmo que os membros estejam offline) - infraestrutura não confiável tem o objetivo de realizar essas propriedades sem a suposição de confiança.
O artigo original do Cwtch definia um conjunto de propriedades que se esperava que os servidores Cwtch fornecessem:
• O Cwtch Server pode ser usado por vários grupos ou apenas um.
• Um servidor Cwtch, sem a colaboração de um membro do grupo, nunca deve aprender a identidade dos participantes de um grupo.
• Um servidor Cwtch nunca deve aprender o conteúdo de qualquer comunicação.
• Um servidor Cwtch nunca deve ser capaz de distinguir mensagens como pertencentes a um grupo específico. Observamos aqui que essas propriedades são um superconjunto dos objetivos de design das estruturas de Recuperação de Informações Privadas.
Melhorias na Eficiência e Segurança
Eficiência do Protocolo
Atualmente, apenas um protocolo conhecido, o PIR ingênuo, atende às propriedades desejadas para garantir a privacidade na comunicação do grupo Cwtch. Este método tem um impacto direto na eficiência da largura de banda, especialmente para usuários em dispositivos móveis. Em resposta a isso, estamos ativamente desenvolvendo novos protocolos que permitem negociar garantias de privacidade e eficiência de maneiras diversas.
Os servidores, no momento desta escrita, permitem o download completo de todas as mensagens armazenadas, bem como uma solicitação para baixar mensagens específicas a partir de uma determinada mensagem. Quando os pares ingressam em um grupo em um novo servidor, eles baixam todas as mensagens do servidor inicialmente e, posteriormente, apenas as mensagens novas.
Mitigação de Análise de Metadados
Essa abordagem permite uma análise moderada de metadados, pois o servidor pode enviar novas mensagens para cada perfil suspeito exclusivo e usar essas assinaturas de mensagens exclusivas para rastrear sessões ao longo do tempo. Essa preocupação é mitigada por dois fatores:
- Os perfis podem atualizar suas conexões a qualquer momento, resultando em uma nova sessão do servidor.
- Os perfis podem ser "ressincronizados" de um servidor a qualquer momento, resultando em uma nova chamada para baixar todas as mensagens. Isso é comumente usado para buscar mensagens antigas de um grupo.
Embora essas medidas imponham limites ao que o servidor pode inferir, ainda não podemos garantir resistência total aos metadados. Para soluções futuras para esse problema, consulte Niwl.
Proteção contra Pares Maliciosos
Os servidores enfrentam o risco de spam gerado por pares, representando uma ameaça significativa à eficácia do sistema Cwtch. Embora tenhamos implementado um mecanismo de proteção contra spam no protótipo do Cwtch, exigindo que os pares realizem alguma prova de trabalho especificada pelo servidor, reconhecemos que essa não é uma solução robusta na presença de um adversário determinado com recursos significativos.
Pacotes de Chaves
Os servidores Cwtch se identificam por meio de pacotes de chaves assinados, contendo uma lista de chaves necessárias para garantir a segurança e resistência aos metadados na comunicação do grupo Cwtch. Esses pacotes de chaves geralmente incluem três chaves: uma chave pública do serviço Tor v3 Onion para o Token Board, uma chave pública do Tor v3 Onion Service para o Token Service e uma chave pública do Privacy Pass.
Para verificar os pacotes de chaves, os perfis que os importam do servidor utilizam o algoritmo trust-on-first-use (TOFU), verificando a assinatura anexada e a existência de todos os tipos de chave. Se o perfil já tiver importado o pacote de chaves do servidor anteriormente, todas as chaves são consideradas iguais.
Configuração prévia do aplicativo para ativar o Relé do Cwtch.
No Android, a hospedagem de servidor não está habilitada, pois essa opção não está disponível devido às limitações dos dispositivos Android. Essa funcionalidade está reservada apenas para servidores hospedados em desktops.
No Android, a única forma direta de importar uma chave de servidor é através do grupo de teste Cwtch, garantindo assim acesso ao servidor Cwtch.
Primeiro passo é Habilitar a opção de grupo no Cwtch que está em fase de testes. Clique na opção no canto superior direito da tela de configuração e pressione o botão para acessar as configurações do Cwtch.
Você pode alterar o idioma para Português do Brasil.Depois, role para baixo e selecione a opção para ativar os experimentos. Em seguida, ative a opção para habilitar o chat em grupo e a pré-visualização de imagens e fotos de perfil, permitindo que você troque sua foto de perfil.
https://pomf2.lain.la/f/eprhj0u3.mp4
Próximo passo é Criar um perfil.
Pressione o + botão de ação no canto inferior direito e selecione "Novo perfil" ou aberta no botão + adicionar novo perfil.
-
Selecione um nome de exibição
-
Selecione se deseja proteger
este perfil e salvo localmente com criptografia forte: Senha: sua conta está protegida de outras pessoas que possam usar este dispositivo
Sem senha: qualquer pessoa que tenha acesso a este dispositivo poderá acessar este perfil.
Preencha sua senha e digite-a novamente
Os perfis são armazenados localmente no disco e criptografados usando uma chave derivada de uma senha conhecida pelo usuário (via pbkdf2).
Observe que, uma vez criptografado e armazenado em disco, a única maneira de recuperar um perfil é recuperando a chave da senha - como tal, não é possível fornecer uma lista completa de perfis aos quais um usuário pode ter acesso até inserir um senha.
https://pomf2.lain.la/f/7p6jfr9r.mp4
O próximo passo é adicionar o FuzzBot, que é um bot de testes e de desenvolvimento.
Contato do FuzzBot: 4y2hxlxqzautabituedksnh2ulcgm2coqbure6wvfpg4gi2ci25ta5ad.
Ao enviar o comando "testgroup-invite" para o FuzzBot, você receberá um convite para entrar no Grupo Cwtch Test. Ao ingressar no grupo, você será automaticamente conectado ao servidor Cwtch. Você pode optar por sair do grupo a qualquer momento ou ficar para conversar e tirar dúvidas sobre o aplicativo e outros assuntos. Depois, você pode configurar seu próprio servidor Cwtch, o que é altamente recomendável. https://pomf2.lain.la/f/x4pm8hm8.mp4
Agora você pode utilizar o aplicativo normalmente. Algumas observações que notei: se houver demora na conexão com outra pessoa, ambas devem estar online. Se ainda assim a conexão não for estabelecida, basta clicar no ícone de reset do Tor para restabelecer a conexão com a outra pessoa.
Uma introdução aos perfis Cwtch.
Com Cwtch você pode criar um ou mais perfis . Cada perfil gera um par de chaves ed25519 aleatório compatível com a Rede Tor.
Este é o identificador que você pode fornecer às pessoas e que elas podem usar para entrar em contato com você via Cwtch.
Cwtch permite criar e gerenciar vários perfis separados. Cada perfil está associado a um par de chaves diferente que inicia um serviço cebola diferente.
Gerenciar Na inicialização, o Cwtch abrirá a tela Gerenciar Perfis. Nessa tela você pode:
- Crie um novo perfil.
- Desbloquear perfis.
- Criptografados existentes.
- Gerenciar perfis carregados.
- Alterando o nome de exibição de um perfil.
- Alterando a senha de um perfil Excluindo um perfil.
- Alterando uma imagem de perfil.
Backup ou exportação de um perfil.
Na tela de gerenciamento de perfil:
-
Selecione o lápis ao lado do perfil que você deseja editar
-
Role para baixo até a parte inferior da tela.
-
Selecione "Exportar perfil"
-
Escolha um local e um nome de arquivo.
5.confirme.
Uma vez confirmado, o Cwtch colocará uma cópia do perfil no local indicado. Este arquivo é criptografado no mesmo nível do perfil.
Este arquivo pode ser importado para outra instância do Cwtch em qualquer dispositivo.
Importando um perfil.
-
Pressione o +botão de ação no canto inferior direito e selecione "Importar perfil"
-
Selecione um arquivo de perfil Cwtch exportado para importar
-
Digite a senha associada ao perfil e confirme.
Uma vez confirmado, o Cwtch tentará descriptografar o arquivo fornecido usando uma chave derivada da senha fornecida. Se for bem-sucedido, o perfil aparecerá na tela Gerenciamento de perfil e estará pronto para uso.
OBSERVAÇÃO Embora um perfil possa ser importado para vários dispositivos, atualmente apenas uma versão de um perfil pode ser usada em todos os dispositivos ao mesmo tempo. As tentativas de usar o mesmo perfil em vários dispositivos podem resultar em problemas de disponibilidade e falhas de mensagens.
Qual é a diferença entre uma conexão ponto a ponto e um grupo cwtch?
As conexões ponto a ponto Cwtch permitem que 2 pessoas troquem mensagens diretamente. As conexões ponto a ponto nos bastidores usam serviços cebola Tor v3 para fornecer uma conexão criptografada e resistente a metadados. Devido a esta conexão direta, ambas as partes precisam estar online ao mesmo tempo para trocar mensagens.
Os Grupos Cwtch permitem que várias partes participem de uma única conversa usando um servidor não confiável (que pode ser fornecido por terceiros ou auto-hospedado). Os operadores de servidores não conseguem saber quantas pessoas estão em um grupo ou o que está sendo discutido. Se vários grupos estiverem hospedados em um único servidor, o servidor não conseguirá saber quais mensagens pertencem a qual grupo sem a conivência de um membro do grupo. Ao contrário das conversas entre pares, as conversas em grupo podem ser conduzidas de forma assíncrona, para que todos num grupo não precisem estar online ao mesmo tempo.
Por que os grupos cwtch são experimentais? Mensagens em grupo resistentes a metadados ainda são um problema em aberto . Embora a versão que fornecemos no Cwtch Beta seja projetada para ser segura e com metadados privados, ela é bastante ineficiente e pode ser mal utilizada. Como tal, aconselhamos cautela ao usá-lo e apenas o fornecemos como um recurso opcional.
Como posso executar meu próprio servidor Cwtch? A implementação de referência para um servidor Cwtch é de código aberto . Qualquer pessoa pode executar um servidor Cwtch, e qualquer pessoa com uma cópia do pacote de chaves públicas do servidor pode hospedar grupos nesse servidor sem que o operador tenha acesso aos metadados relacionados ao grupo .
https://git.openprivacy.ca/cwtch.im/server
https://docs.openprivacy.ca/cwtch-security-handbook/server.html
Como posso desligar o Cwtch? O painel frontal do aplicativo possui um ícone do botão "Shutdown Cwtch" (com um 'X'). Pressionar este botão irá acionar uma caixa de diálogo e, na confirmação, o Cwtch será desligado e todos os perfis serão descarregados.
Suas doações podem fazer a diferença no projeto Cwtch? O Cwtch é um projeto dedicado a construir aplicativos que preservam a privacidade, oferecendo comunicação de grupo resistente a metadados. Além disso, o projeto também desenvolve o Cofre, formulários da web criptografados para ajudar mútua segura. Suas contribuições apoiam iniciativas importantes, como a divulgação de violações de dados médicos em Vancouver e pesquisas sobre a segurança do voto eletrônico na Suíça. Ao doar, você está ajudando a fechar o ciclo, trabalhando com comunidades marginalizadas para identificar e corrigir lacunas de privacidade. Além disso, o projeto trabalha em soluções inovadoras, como a quebra de segredos através da criptografia de limite para proteger sua privacidade durante passagens de fronteira. E também tem a infraestrutura: toda nossa infraestrutura é open source e sem fins lucrativos. Conheça também o Fuzzytags, uma estrutura criptográfica probabilística para marcação resistente a metadados. Sua doação é crucial para continuar o trabalho em prol da privacidade e segurança online. Contribua agora com sua doação
https://openprivacy.ca/donate/
onde você pode fazer sua doação em bitcoin e outras moedas, e saiba mais sobre os projetos. https://openprivacy.ca/work/
Link sobre Cwtch
https://cwtch.im/
https://git.openprivacy.ca/cwtch.im/cwtch
https://docs.cwtch.im/docs/intro
https://docs.openprivacy.ca/cwtch-security-handbook/
Baixar #CwtchDev
cwtch.im/download/
https://play.google.com/store/apps/details?id=im.cwtch.flwtch
-
 @ 39cc53c9:27168656
2025-05-27 09:21:40
@ 39cc53c9:27168656
2025-05-27 09:21:40“The future is there... staring back at us. Trying to make sense of the fiction we will have become.” — William Gibson.
This month is the 4th anniversary of kycnot.me. Thank you for being here.
Fifteen years ago, Satoshi Nakamoto introduced Bitcoin, a peer-to-peer electronic cash system: a decentralized currency free from government and institutional control. Nakamoto's whitepaper showed a vision for a financial system based on trustless transactions, secured by cryptography. Some time forward and KYC (Know Your Customer), AML (Anti-Money Laundering), and CTF (Counter-Terrorism Financing) regulations started to come into play.
What a paradox: to engage with a system designed for decentralization, privacy, and independence, we are forced to give away our personal details. Using Bitcoin in the economy requires revealing your identity, not just to the party you interact with, but also to third parties who must track and report the interaction. You are forced to give sensitive data to entities you don't, can't, and shouldn't trust. Information can never be kept 100% safe; there's always a risk. Information is power, who knows about you has control over you.
Information asymmetry creates imbalances of power. When entities have detailed knowledge about individuals, they can manipulate, influence, or exploit this information to their advantage. The accumulation of personal data by corporations and governments enables extensive surveillances.
Such practices, moreover, exclude individuals from traditional economic systems if their documentation doesn't meet arbitrary standards, reinforcing a dystopian divide. Small businesses are similarly burdened by the costs of implementing these regulations, hindering free market competition^1:
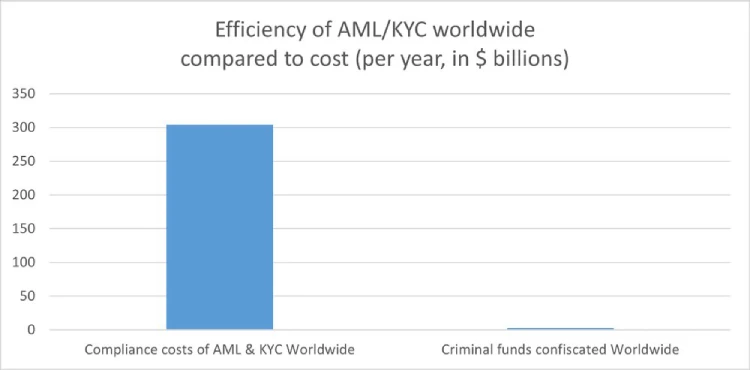
How will they keep this information safe? Why do they need my identity? Why do they force businesses to enforce such regulations? It's always for your safety, to protect you from the "bad". Your life is perpetually in danger: terrorists, money launderers, villains... so the government steps in to save us.
‟Hush now, baby, baby, don't you cry Mamma's gonna make all of your nightmares come true Mamma's gonna put all of her fears into you Mamma's gonna keep you right here, under her wing She won't let you fly, but she might let you sing Mamma's gonna keep baby cosy and warm” — Mother, Pink Floyd
We must resist any attack on our privacy and freedom. To do this, we must collaborate.
If you have a service, refuse to ask for KYC; find a way. Accept cryptocurrencies like Bitcoin and Monero. Commit to circular economies. Remove the need to go through the FIAT system. People need fiat money to use most services, but we can change that.
If you're a user, donate to and prefer using services that accept such currencies. Encourage your friends to accept cryptocurrencies as well. Boycott FIAT system to the greatest extent you possibly can.
This may sound utopian, but it can be achieved. This movement can't be stopped. Go kick the hornet's nest.
“We must defend our own privacy if we expect to have any. We must come together and create systems which allow anonymous transactions to take place. People have been defending their own privacy for centuries with whispers, darkness, envelopes, closed doors, secret handshakes, and couriers. The technologies of the past did not allow for strong privacy, but electronic technologies do.” — Eric Hughes, A Cypherpunk's Manifesto
The anniversary
Four years ago, I began exploring ways to use crypto without KYC. I bookmarked a few favorite services and thought sharing them to the world might be useful. That was the first version of kycnot.me — a simple list of about 15 services. Since then, I've added services, rewritten it three times, and improved it to what it is now.
kycnot.me has remained 100% independent and 100% open source^2 all these years. I've received offers to buy the site, all of which I have declined and will continue to decline. It has been DDoS attacked many times, but we made it through. I have also rewritten the whole site almost once per year (three times in four years).
The code and scoring algorithm are open source (contributions are welcome) and I can't arbitrarly change a service's score without adding or removing attributes, making any arbitrary alterations obvious if they were fake. You can even see the score summary for any service's score.
I'm a one-person team, dedicating my free time to this project. I hope to keep doing so for many more years. Again, thank you for being part of this.
-
 @ 39cc53c9:27168656
2025-05-27 09:21:37
@ 39cc53c9:27168656
2025-05-27 09:21:37After almost 3 months of work, we've completed the redesign of kycnot.me. More modern and with many new features.
Privacy remains the foundation - everything still works with JavaScript disabled. If you enable JS, you will get some nice-to-have features like lazy loading and smoother page transitions, but nothing essential requires it.
User Accounts
We've introduced user accounts that require zero personal information:
- Secret user tokens - no email, no phone number, no personal data
- Randomly generated usernames for default privacy and fairness
- Karma system that rewards contributions and unlocks features: custom display names, profile pictures, and more.
Reviews and Community Discussions
On the previous sites, I was using third party open source tools for the comments and discussions. This time, I've built my own from scratch, fully integrated into the site, without JavaScript requirements.
Everyone can share their experiences and help others make informed decisions:
- Ratings: Comments can have a 1-5 star rating attached. You can have one rating per service and it will affect the overall user score.
- Discussions: These are normal comments, you can add them on any listed service.
Comment Moderation
I was strugling to keep up with moderation on the old site. For this, we've implemented an AI-powered moderation system that:
- Auto-approves legitimate comments instantly
- Flags suspicious content for human review
- Keeps discussions valuable by minimizing spam
The AI still can mark comments for human review, but most comments will get approved automatically by this system. The AI also makes summaries of the comments to help you understand the overall sentiment of the community.
Powerful Search & Filtering
Finding exactly what you need is now easier:
- Advanced filtering system with many parameters. You can even filter by attributes to pinpoint services with specific features.
The results are dynamic and shuffle services with identical scores for fairness.
See all listings
Listings are now added as 'Community Contributed' by default. This means that you can still find them in the search results, but they will be clearly marked as such.
Updated Scoring System
New dual-score approach provides more nuanced service evaluations:
- Privacy Score: Measures how well a service protects your personal information and data
-
Trust Score: Assesses reliability, security, and overall reputation
-
Combined into a weighted Overall Score for quick comparisons
- Completely transparent and open source calculation algorithm. No manual tweaking or hidden factors.
AI-Powered Terms of Service Analysis
Basically, a TLDR summary for Terms of Service:
- Automated system extracts the most important points from complex ToS documents
- Clear summaries
- Updated monthly to catch any changes
The ToS document is hashed and only will be updated if there are any changes.
Service Events and Timelines
Track the complete history of any service, on each service page you can see the timeline of events. There are two types of events:
- Automatic events: Created by the system whenever something about a service changes, like its description, supported currencies, attributes, verification status…
- Manual events: Added by admins when there’s important news, such as a service going offline, being hacked, acquired, shut down, or other major updates.
There is also a global timeline view available at /events
Notification System
Since we now have user accounts, we built a notifiaction system so you can stay informed about anything:
- Notifications for comment replies and status changes
- Watch any comment to get notified for new replies.
- Subscribe to services to monitor events and updates
- Notification customization.
Coming soon: Third-party privacy-preserving notifications integration with Telegram, Ntfy.sh, webhooks...
Service Suggestions
Anyone with an account can suggest a new service via the suggestion form. After submitting, you'll receive a tracking page where you can follow the status of your suggestion and communicate directly with admins.
All new suggestions start as "unlisted" — they won't appear in search results until reviewed. Our team checks each submission to ensure it's not spam or inappropriate. If similar services already exist, you'll be shown possible duplicates and can choose to submit your suggestion as an edit instead.
You can always check the progress of your suggestion, respond to moderator questions, and see when it goes live, everything will also be notified to your account. This process ensures high-quality listings and a collaborative approach to building the directory.
These are some of the main features we already have, but there are many more small changes and improvements that you will find when using the site.
What's Next?
This is just the beginning. We will be constantly working to improve KYCnot.me and add more features that help you preserve your privacy.
Remember: True financial freedom requires the right to privacy. Stay KYC-free!
-
 @ b83a28b7:35919450
2025-05-16 19:23:58
@ b83a28b7:35919450
2025-05-16 19:23:58This article was originally part of the sermon of Plebchain Radio Episode 110 (May 2, 2025) that nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpqtvqc82mv8cezhax5r34n4muc2c4pgjz8kaye2smj032nngg52clq7fgefr and I did with nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7ct4w35zumn0wd68yvfwvdhk6tcqyzx4h2fv3n9r6hrnjtcrjw43t0g0cmmrgvjmg525rc8hexkxc0kd2rhtk62 and nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpq4wxtsrj7g2jugh70pfkzjln43vgn4p7655pgky9j9w9d75u465pqahkzd0 of the nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcqyqwfvwrccp4j2xsuuvkwg0y6a20637t6f4cc5zzjkx030dkztt7t5hydajn
Listen to the full episode here:
<https://fountain.fm/episode/Ln9Ej0zCZ5dEwfo8w2Ho>
Bitcoin has always been a narrative revolution disguised as code. White paper, cypherpunk lore, pizza‑day legends - every block is a paragraph in the world’s most relentless epic. But code alone rarely converts the skeptic; it’s the camp‑fire myth that slips past the prefrontal cortex and shakes hands with the limbic system. People don’t adopt protocols first - they fall in love with protagonists.
Early adopters heard the white‑paper hymn, but most folks need characters first: a pizza‑day dreamer; a mother in a small country, crushed by the cost of remittance; a Warsaw street vendor swapping złoty for sats. When their arcs land, the brain releases a neurochemical OP_RETURN which says, “I belong in this plot.” That’s the sly roundabout orange pill: conviction smuggled inside catharsis.
That’s why, from 22–25 May in Warsaw’s Kinoteka, the Bitcoin Film Fest is loading its reels with rebellion. Each documentary, drama, and animated rabbit‑hole is a stealth wallet, zipping conviction straight into the feels of anyone still clasped within the cold claw of fiat. You come for the plot, you leave checking block heights.
Here's the clip of the sermon from the episode:
nostr:nevent1qvzqqqqqqypzpwp69zm7fewjp0vkp306adnzt7249ytxhz7mq3w5yc629u6er9zsqqsy43fwz8es2wnn65rh0udc05tumdnx5xagvzd88ptncspmesdqhygcrvpf2
-
 @ 04c915da:3dfbecc9
2025-05-16 18:06:46
@ 04c915da:3dfbecc9
2025-05-16 18:06:46Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Using stolen bitcoin for the reserve creates a perverse incentive. If governments see bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:59:23
@ 04c915da:3dfbecc9
2025-05-16 17:59:23Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ 5ea46480:450da5bd
2025-05-27 08:23:58
@ 5ea46480:450da5bd
2025-05-27 08:23:58Understanding or grasping Nostr can be deceptively difficult. At the very least it is non-trivial. At first glance, looking at NIP-01, the protocol is rather straight forward. But those are just the basics; yes the beauty of Nostr is its ‘simplicity’, but that does not mean the system that results from it is not complex. Conway's Game of Life only has a hand full of rules, yet you can, in theory at least, create any complex system imaginable. And this is where the deception lies; the less you define from the outset, the more you imply on what follows.
It appears that as it stands, Nostr suffers from this deceptiveness. You can reason through all these implications, but that is still an exercise that has to be performed and where mistakes can be made. Worse, this exercise has been a group effort from the start that is still in progress. Currently there is no clear cut ‘authoritative’ example of all the implications that have been ‘discovered’ thus far.
A good example of the implications following Nostr’s primitives is what we now refer to as the ‘outbox model’. The reason we ‘now’ refer to it as such, is because initially it was called the ‘Gossip model’ derived from the client that first implemented the idea. Outbox is fundamental to Nostr, but it was never explicitly stated in the initial protocol description. The result is that roughly five years into this Nostr endeavor, it is still not universally implemented; worse yet, some developers appear to be in no rush to do so. Now the reason they will give you is probably one based on priority, yet I can’t shake the feeling that they apparently don’t ‘get it’.
My point here is not to play some blame game or hold anyone to account. I am just concluding they don’t actually get the new paradigm that we have all stumbled into. To expand on this specific outbox example, its significance only becomes really apparent further along in the ‘reasoning through all the implications’ exercise. In relation to one aspect, but there are more: The point is not ‘just’ censorship-resistance for users, but the freedom for relays that comes with it to apply whatever policy on what they store and make available; it is this discrimination or curation that can add value by making finding relevant information easier in a straightforward manner. But it relies on outbox to avoid isolation; something that only becomes apparent once you are reasoning through all the implications on how we discover and consume content.
To be clear, this piece is not supposed to a crusade on the outbox model, my point here is that there is an inherent logic to Nostr stemming from putting cryptography front and center. It is a logic that has to be applied and will subsequently carry you through all the challenges we face in reconstructing the entirety of the web. This is not to say there is only one obvious path, and different schools of thought are bound to emerge. But it behooves us all, faced with this new paradigm, to continuously reflect on the mental image we have cultivated of what Nostr is; actively re-performing that exercise of exploring the implications this simple set of protocol rules creates.
Unfortunately I can not escape my own folly. After all, I am just an armchair asshole that never wrote a single line of code in his life. Obviously this minds-eye bullshit is not even half the story, the bulk of the effort is translating it into software, the tangible, the real. It is in that effort ultimately the real exploration of this paradigm occurs. All I can do is build castles in the sky.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:51:54
@ 04c915da:3dfbecc9
2025-05-16 17:51:54In much of the world, it is incredibly difficult to access U.S. dollars. Local currencies are often poorly managed and riddled with corruption. Billions of people demand a more reliable alternative. While the dollar has its own issues of corruption and mismanagement, it is widely regarded as superior to the fiat currencies it competes with globally. As a result, Tether has found massive success providing low cost, low friction access to dollars. Tether claims 400 million total users, is on track to add 200 million more this year, processes 8.1 million transactions daily, and facilitates $29 billion in daily transfers. Furthermore, their estimates suggest nearly 40% of users rely on it as a savings tool rather than just a transactional currency.
Tether’s rise has made the company a financial juggernaut. Last year alone, Tether raked in over $13 billion in profit, with a lean team of less than 100 employees. Their business model is elegantly simple: hold U.S. Treasuries and collect the interest. With over $113 billion in Treasuries, Tether has turned a straightforward concept into a profit machine.
Tether’s success has resulted in many competitors eager to claim a piece of the pie. This has triggered a massive venture capital grift cycle in USD tokens, with countless projects vying to dethrone Tether. Due to Tether’s entrenched network effect, these challengers face an uphill battle with little realistic chance of success. Most educated participants in the space likely recognize this reality but seem content to perpetuate the grift, hoping to cash out by dumping their equity positions on unsuspecting buyers before they realize the reality of the situation.
Historically, Tether’s greatest vulnerability has been U.S. government intervention. For over a decade, the company operated offshore with few allies in the U.S. establishment, making it a major target for regulatory action. That dynamic has shifted recently and Tether has seized the opportunity. By actively courting U.S. government support, Tether has fortified their position. This strategic move will likely cement their status as the dominant USD token for years to come.
While undeniably a great tool for the millions of users that rely on it, Tether is not without flaws. As a centralized, trusted third party, it holds the power to freeze or seize funds at its discretion. Corporate mismanagement or deliberate malpractice could also lead to massive losses at scale. In their goal of mitigating regulatory risk, Tether has deepened ties with law enforcement, mirroring some of the concerns of potential central bank digital currencies. In practice, Tether operates as a corporate CBDC alternative, collaborating with authorities to surveil and seize funds. The company proudly touts partnerships with leading surveillance firms and its own data reveals cooperation in over 1,000 law enforcement cases, with more than $2.5 billion in funds frozen.
The global demand for Tether is undeniable and the company’s profitability reflects its unrivaled success. Tether is owned and operated by bitcoiners and will likely continue to push forward strategic goals that help the movement as a whole. Recent efforts to mitigate the threat of U.S. government enforcement will likely solidify their network effect and stifle meaningful adoption of rival USD tokens or CBDCs. Yet, for all their achievements, Tether is simply a worse form of money than bitcoin. Tether requires trust in a centralized entity, while bitcoin can be saved or spent without permission. Furthermore, Tether is tied to the value of the US Dollar which is designed to lose purchasing power over time, while bitcoin, as a truly scarce asset, is designed to increase in purchasing power with adoption. As people awaken to the risks of Tether’s control, and the benefits bitcoin provides, bitcoin adoption will likely surpass it.
-
 @ 84b0c46a:417782f5
2025-05-27 08:19:49
@ 84b0c46a:417782f5
2025-05-27 08:19:49Simple Long Form Content Editor (NIP-23)
機能
-
nostr:npub1sjcvg64knxkrt6ev52rywzu9uzqakgy8ehhk8yezxmpewsthst6sw3jqcw や、 nostr:nevent1qvzqqqqqqypzq4jsz7zew5j7jr4pdfxh483nwq9vyw9ph6wm706sjwrzj2we58nqqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyxhwumn8ghj7mn0wvhxcmmvqqsgcn99jyn5tevxz5zxsrkd7h0sx8fwnqztula423xh83j9wau7cms3vg9c7 のようにnostr:要素を挿入できる (メニューのNアイコンから挿入またはnostr:note~~のように手動で入力)
-
:monoice:のようにカスタム絵文字を挿入できる(メニューの🙂アイコンから)
:monopaca_kao:
:kubipaca_karada:
- 新規記事作成と、既存記事の修正ができる
やることやったこと
-
[x] nostr:を投稿するときにtagにいれる
-
[x] 画像をアップロードできるようにする(NIP-96)
 できる
できる - [x] 投稿しましたログとかをトースト的なやつでだすようにする
- [ ] レイアウトを整える
- [ ] あとなんか
-
-
 @ 04c915da:3dfbecc9
2025-05-16 17:12:05
@ 04c915da:3dfbecc9
2025-05-16 17:12:05One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ b7274d28:c99628cb
2025-05-27 07:07:33
@ b7274d28:c99628cb
2025-05-27 07:07:33A few months ago, a nostrich was switching from iOS to Android and asked for suggestions for #Nostr apps to try out. nostr:npub18ams6ewn5aj2n3wt2qawzglx9mr4nzksxhvrdc4gzrecw7n5tvjqctp424 offered the following as his response:
nostr:nevent1qvzqqqqqqypzq0mhp4ja8fmy48zuk5p6uy37vtk8tx9dqdwcxm32sy8nsaa8gkeyqydhwumn8ghj7un9d3shjtnwdaehgunsd3jkyuewvdhk6tcpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhszythwden5te0dehhxarj9emkjmn99uqzpwwts6n28eyvjpcwvu5akkwu85eg92dpvgw7cgmpe4czdadqvnv984rl0z
Yes. #Android users are fortunate to have some powerful Nostr apps and tools at our disposal that simply have no comparison over on the iOS side. However, a tool is only as good as the knowledge of the user, who must have an understanding of how best to wield it for maximum effect. This fact was immediately evidenced by replies to Derek asking, "What is the use case for Citrine?" and "This is the first time I'm hearing about Citrine and Pokey. Can you give me links for those?"
Well, consider this tutorial your Nostr starter-kit for Android. We'll go over installing and setting up Amber, Amethyst, Citrine, and Pokey, and as a bonus we'll be throwing in the Zapstore and Coinos to boot. We will assume no previous experience with any of the above, so if you already know all about one or more of these apps, you can feel free to skip that tutorial.
So many apps...
You may be wondering, "Why do I need so many apps to use Nostr?" That's perfectly valid, and the honest answer is, you don't. You can absolutely just install a Nostr client from the Play Store, have it generate your Nostr identity for you, and stick with the default relays already set up in that app. You don't even need to connect a wallet, if you don't want to. However, you won't experience all that Nostr has to offer if that is as far as you go, any more than you would experience all that Italian cuisine has to offer if you only ever try spaghetti.
Nostr is not just one app that does one thing, like Facebook, Twitter, or TikTok. It is an entire ecosystem of applications that are all built on top of a protocol that allows them to be interoperable. This set of tools will help you make the most out of that interoperability, which you will never get from any of the big-tech social platforms. It will provide a solid foundation for you to build upon as you explore more and more of what Nostr has to offer.
So what do these apps do?

Fundamental to everything you do on Nostr is the need to cryptographically sign with your private key. If you aren't sure what that means, just imagine that you had to enter your password every time you hit the "like" button on Facebook, or every time you commented on the latest dank meme. That would get old really fast, right? That's effectively what Nostr requires, but on steroids.
To keep this from being something you manually have to do every 5 seconds when you post a note, react to someone else's note, or add a comment, Nostr apps can store your private key and use it to sign behind the scenes for you. This is very convenient, but it means you are trusting that app to not do anything with your private key that you don't want it to. You are also trusting it to not leak your private key, because anyone who gets their hands on it will be able to post as you, see your private messages, and effectively be you on Nostr. The more apps you give your private key to, the greater your risk that it will eventually be compromised.
Enter #Amber, an application that will store your private key in only one app, and all other compatible Nostr apps can communicate with it to request a signature, without giving any of those other apps access to your private key.
Most Nostr apps for Android now support logging in and signing with Amber, and you can even use it to log into apps on other devices, such as some of the web apps you use on your PC. It's an incredible tool given to us by nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5, and only available for Android users. Those on iPhone are incredibly jealous that they don't have anything comparable, yet.

Speaking of nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5, the next app is also one of his making.
All Nostr data is stored on relays, which are very simple servers that Nostr apps read notes from and write notes to. In most forms of social media, it can be a pain to get your own data out to keep a backup. That's not the case on Nostr. Anyone can run their own relay, either for the sake of backing up their personal notes, or for others to post their notes to, as well.
Since Nostr notes take up very little space, you can actually run a relay on your phone. I have been on Nostr for almost 2 and a half years, and I have 25,000+ notes of various kinds on my relay, and a backup of that full database is just 24MB on my phone's storage.
Having that backup can save your bacon if you try out a new Nostr client and it doesn't find your existing follow list for some reason, so it writes a new one and you suddenly lose all of the people you were following. Just pop into your #Citrine relay, confirm it still has your correct follow list or import it from a recent backup, then have Citrine restore it. Done.
Additionally, there are things you may want to only save to a relay you control, such as draft messages that you aren't ready to post publicly, or eCash tokens, which can actually be saved to Nostr relays now. Citrine can also be used with Amber for signing into certain Nostr applications that use a relay to communicate with Amber.
If you are really adventurous, you can also expose Citrine over Tor to be used as an outbox relay, or used for peer-to-peer private messaging, but that is far more involved than the scope of this tutorial series.

You can't get far in Nostr without a solid and reliable client to interact with. #Amethyst is the client we will be using for this tutorial because there simply isn't another Android client that comes close, so far. Moreover, it can be a great client for new users to get started on, and yet it has a ton of features for power-users to take advantage of as well.
There are plenty of other good clients to check out over time, such as Coracle, YakiHonne, Voyage, Olas, Flotilla and others, but I keep coming back to Amethyst, and by the time you finish this tutorial, I think you'll see why. nostr:npub1gcxzte5zlkncx26j68ez60fzkvtkm9e0vrwdcvsjakxf9mu9qewqlfnj5z and others who have contributed to Amethyst have really built something special in this client, and it just keeps improving with every update that's shipped.

Most social media apps have some form of push notifications, and some Nostr apps do, too. Where the issue comes in is that Nostr apps are all interoperable. If you have more than one application, you're going to have both of them notifying you. Nostr users are known for having five or more Nostr apps that they use regularly. If all of them had notifications turned on, it would be a nightmare. So maybe you limit it to only one of your Nostr apps having notifications turned on, but then you are pretty well locked-in to opening that particular app when you tap on the notification.
Pokey, by nostr:npub1v3tgrwwsv7c6xckyhm5dmluc05jxd4yeqhpxew87chn0kua0tjzqc6yvjh, solves this issue, allowing you to turn notifications off for all of your Nostr apps, and have Pokey handle them all for you. Then, when you tap on a Pokey notification, you can choose which Nostr app to open it in.
Pokey also gives you control over the types of things you want to be notified about. Maybe you don't care about reactions, and you just want to know about zaps, comments, and direct messages. Pokey has you covered. It even supports multiple accounts, so you can get notifications for all the npubs you control.

One of the most unique and incredibly fun aspects of Nostr is the ability to send and receive #zaps. Instead of merely giving someone a 👍️ when you like something they said, you can actually send them real value in the form of sats, small portions of a Bitcoin. There is nothing quite like the experience of receiving your first zap and realizing that someone valued what you said enough to send you a small amount (and sometimes not so small) of #Bitcoin, the best money mankind has ever known.
To be able to have that experience, though, you are going to need a wallet that can send and receive zaps, and preferably one that is easy to connect to Nostr applications. My current preference for that is Alby Hub, but not everyone wants to deal with all that comes along with running a #Lightning node. That being the case, I have opted to use nostr:npub1h2qfjpnxau9k7ja9qkf50043xfpfy8j5v60xsqryef64y44puwnq28w8ch for this tutorial, because they offer one of the easiest wallets to set up, and it connects to most Nostr apps by just copy/pasting a connection string from the settings in the wallet into the settings in your Nostr app of choice.
Additionally, even though #Coinos is a custodial wallet, you can have it automatically transfer any #sats over a specified threshold to a separate wallet, allowing you to mitigate the custodial risk without needing to keep an eye on your balance and make the transfer manually.

Most of us on Android are used to getting all of our mobile apps from one souce: the Google Play Store. That's not possible for this tutorial series. Only one of the apps mentioned above is available in Google's permissioned playground. However, on Android we have the advantage of being able to install whatever we want on our device, just by popping into our settings and flipping a toggle. Indeed, thumbing our noses at big-tech is at the heart of the Nostr ethos, so why would we make ourselves beholden to Google for installing Nostr apps?
The nostr:npub10r8xl2njyepcw2zwv3a6dyufj4e4ajx86hz6v4ehu4gnpupxxp7stjt2p8 is an alternative app store made by nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9 as a resource for all sorts of open-source apps, but especially Nostr apps. What is more, you can log in with Amber, connect a wallet like Coinos, and support the developers of your favorite Nostr apps directly within the #Zapstore by zapping their app releases.
One of the biggest features of the Zapstore is the fact that developers can cryptographically sign their app releases using their Nostr keys, so you know that the app you are downloading is the one they actually released and hasn't been altered in any way. The Zapstore will warn you and won't let you install the app if the signature is invalid.
Getting Started
Since the Zapstore will be the source we use for installing most of the other apps mentioned, we will start with installing the Zapstore.
We will then use the Zapstore to install Amber and set it up with our Nostr account, either by creating a new private key, or by importing one we already have. We'll also use it to log into the Zapstore.
Next, we will install Amethyst from the Zapstore and log into it via Amber.
After this, we will install Citrine from the Zapstore and add it as a local relay on Amethyst.
Because we want to be able to send and receive zaps, we will set up a wallet with CoinOS and connect it to Amethyst and the Zapstore using Nostr Wallet Connect.
Finally, we will install Pokey using the Zapstore, log into it using Amber, and set up the notifications we want to receive.
By the time you are done with this series, you will have a great head-start on your Nostr journey compared to muddling through it all on your own. Moreover, you will have developed a familiarity with how things generally work on Nostr that can be applied to other apps you try out in the future.
Continue to Part 2: The Zapstore. Nostr Link: nostr:naddr1qvzqqqr4gupzpde8f55w86vrhaeqmd955y4rraw8aunzxgxstsj7eyzgntyev2xtqydhwumn8ghj7un9d3shjtnzwf5kw6r5vfhkcapwdejhgtcqp5cnwdphxv6rwwp3xvmnzvqgty5au
-
 @ 04c915da:3dfbecc9
2025-05-15 15:31:45
@ 04c915da:3dfbecc9
2025-05-15 15:31:45Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 08f96856:ffe59a09
2025-05-15 01:17:18
@ 08f96856:ffe59a09
2025-05-15 01:17:18เมื่อพูดถึง Bitcoin Standard หลายคนมักนึกถึงภาพโลกอนาคตที่ทุกคนใช้บิตคอยน์ซื้อกาแฟหรือของใช้ในชีวิตประจำวัน ภาพแบบนั้นดูเหมือนไกลตัวและเป็นไปไม่ได้ในความเป็นจริง หลายคนถึงกับพูดว่า “คงไม่ทันเห็นในช่วงชีวิตนี้หรอก” แต่ในมุมมองของผม Bitcoin Standard อาจไม่ได้เริ่มต้นจากการที่เราจ่ายบิตคอยน์โดยตรงในร้านค้า แต่อาจเริ่มจากบางสิ่งที่เงียบกว่า ลึกกว่า และเกิดขึ้นแล้วในขณะนี้ นั่นคือ การล่มสลายทีละน้อยของระบบเฟียตที่เราใช้กันอยู่
ระบบเงินที่อิงกับอำนาจรัฐกำลังเข้าสู่ช่วงขาลง รัฐบาลทั่วโลกกำลังจมอยู่ในภาระหนี้ระดับประวัติการณ์ แม้แต่ประเทศมหาอำนาจก็เริ่มแสดงสัญญาณของภาวะเสี่ยงผิดนัดชำระหนี้ อัตราเงินเฟ้อกลายเป็นปัญหาเรื้อรังที่ไม่มีท่าทีจะหายไป ธนาคารที่เคยโอนฟรีเริ่มกลับมาคิดค่าธรรมเนียม และประชาชนก็เริ่มรู้สึกถึงการเสื่อมศรัทธาในระบบการเงินดั้งเดิม แม้จะยังพูดกันไม่เต็มเสียงก็ตาม
ในขณะเดียวกัน บิตคอยน์เองก็กำลังพัฒนาแบบเงียบ ๆ เงียบ... แต่ไม่เคยหยุด โดยเฉพาะในระดับ Layer 2 ที่เริ่มแสดงศักยภาพอย่างจริงจัง Lightning Network เป็น Layer 2 ที่เปิดใช้งานมาได้ระยะเวลสหนึ่ง และยังคงมีบทบาทสำคัญที่สุดในระบบนิเวศของบิตคอยน์ มันทำให้การชำระเงินเร็วขึ้น มีต้นทุนต่ำ และไม่ต้องบันทึกทุกธุรกรรมลงบล็อกเชน เครือข่ายนี้กำลังขยายตัวทั้งในแง่ของโหนดและการใช้งานจริงทั่วโลก
ขณะเดียวกัน Layer 2 ทางเลือกอื่นอย่าง Ark Protocol ก็กำลังพัฒนาเพื่อตอบโจทย์ด้านความเป็นส่วนตัวและประสบการณ์ใช้งานที่ง่าย BitVM เปิดแนวทางใหม่ให้บิตคอยน์รองรับ smart contract ได้ในระดับ Turing-complete ซึ่งทำให้เกิดความเป็นไปได้ในกรณีใช้งานอีกมากมาย และเทคโนโลยีที่น่าสนใจอย่าง Taproot Assets, Cashu และ Fedimint ก็ทำให้การออกโทเคนหรือสกุลเงินที่อิงกับบิตคอยน์เป็นจริงได้บนโครงสร้างของบิตคอยน์เอง
เทคโนโลยีเหล่านี้ไม่ใช่การเติบโตแบบปาฏิหาริย์ แต่มันคืบหน้าอย่างต่อเนื่องและมั่นคง และนั่นคือเหตุผลที่มันจะ “อยู่รอด” ได้ในระยะยาว เมื่อฐานของความน่าเชื่อถือไม่ใช่บริษัท รัฐบาล หรือทุน แต่คือสิ่งที่ตรวจสอบได้และเปลี่ยนกฎไม่ได้
แน่นอนว่าบิตคอยน์ต้องแข่งขันกับ stable coin, เงินดิจิทัลของรัฐ และ cryptocurrency อื่น ๆ แต่สิ่งที่ทำให้มันเหนือกว่านั้นไม่ใช่ฟีเจอร์ หากแต่เป็นความทนทาน และความมั่นคงของกฎที่ไม่มีใครเปลี่ยนได้ ไม่มีทีมพัฒนา ไม่มีบริษัท ไม่มีประตูปิด หรือการยึดบัญชี มันยืนอยู่บนคณิตศาสตร์ พลังงาน และเวลา
หลายกรณีใช้งานที่เคยถูกทดลองในโลกคริปโตจะค่อย ๆ เคลื่อนเข้ามาสู่บิตคอยน์ เพราะโครงสร้างของมันแข็งแกร่งกว่า ไม่ต้องการทีมพัฒนาแกนกลาง ไม่ต้องพึ่งกลไกเสี่ยงต่อการผูกขาด และไม่ต้องการ “ความเชื่อใจ” จากใครเลย
Bitcoin Standard ที่ผมพูดถึงจึงไม่ใช่การเปลี่ยนแปลงแบบพลิกหน้ามือเป็นหลังมือ แต่คือการ “เปลี่ยนฐานของระบบ” ทีละชั้น ระบบการเงินใหม่ที่อิงอยู่กับบิตคอยน์กำลังเกิดขึ้นแล้ว มันไม่ใช่โลกที่ทุกคนถือเหรียญบิตคอยน์ แต่มันคือโลกที่คนใช้อาจไม่รู้ตัวด้วยซ้ำว่า “สิ่งที่เขาใช้นั้นอิงอยู่กับบิตคอยน์”
ผู้คนอาจใช้เงินดิจิทัลที่สร้างบน Layer 3 หรือ Layer 4 ผ่านแอป ผ่านแพลตฟอร์ม หรือผ่านสกุลเงินใหม่ที่ดูไม่ต่างจากเดิม แต่เบื้องหลังของระบบจะผูกไว้กับบิตคอยน์
และถ้ามองในเชิงพัฒนาการ บิตคอยน์ก็เหมือนกับอินเทอร์เน็ต ครั้งหนึ่งอินเทอร์เน็ตก็ถูกมองว่าเข้าใจยาก ต้องพิมพ์ http ต้องรู้จัก TCP/IP ต้องตั้ง proxy เอง แต่ปัจจุบันผู้คนใช้งานอินเทอร์เน็ตโดยไม่รู้ว่าเบื้องหลังมีอะไรเลย บิตคอยน์กำลังเดินตามเส้นทางเดียวกัน โปรโตคอลกำลังถอยออกจากสายตา และวันหนึ่งเราจะ “ใช้มัน” โดยไม่ต้องรู้ว่ามันคืออะไร
หากนับจากช่วงเริ่มต้นของอินเทอร์เน็ตในยุค 1990 จนกลายเป็นโครงสร้างหลักของโลกในสองทศวรรษ เส้นเวลาของบิตคอยน์ก็กำลังเดินตามรอยเท้าของอินเทอร์เน็ต และถ้าเราเชื่อว่าวัฏจักรของเทคโนโลยีมีจังหวะของมันเอง เราก็จะรู้ว่า Bitcoin Standard นั้นไม่ใช่เรื่องของอนาคตไกลโพ้น แต่มันเกิดขึ้นแล้ว
-
 @ 7f6db517:a4931eda
2025-05-27 05:01:34
@ 7f6db517:a4931eda
2025-05-27 05:01:34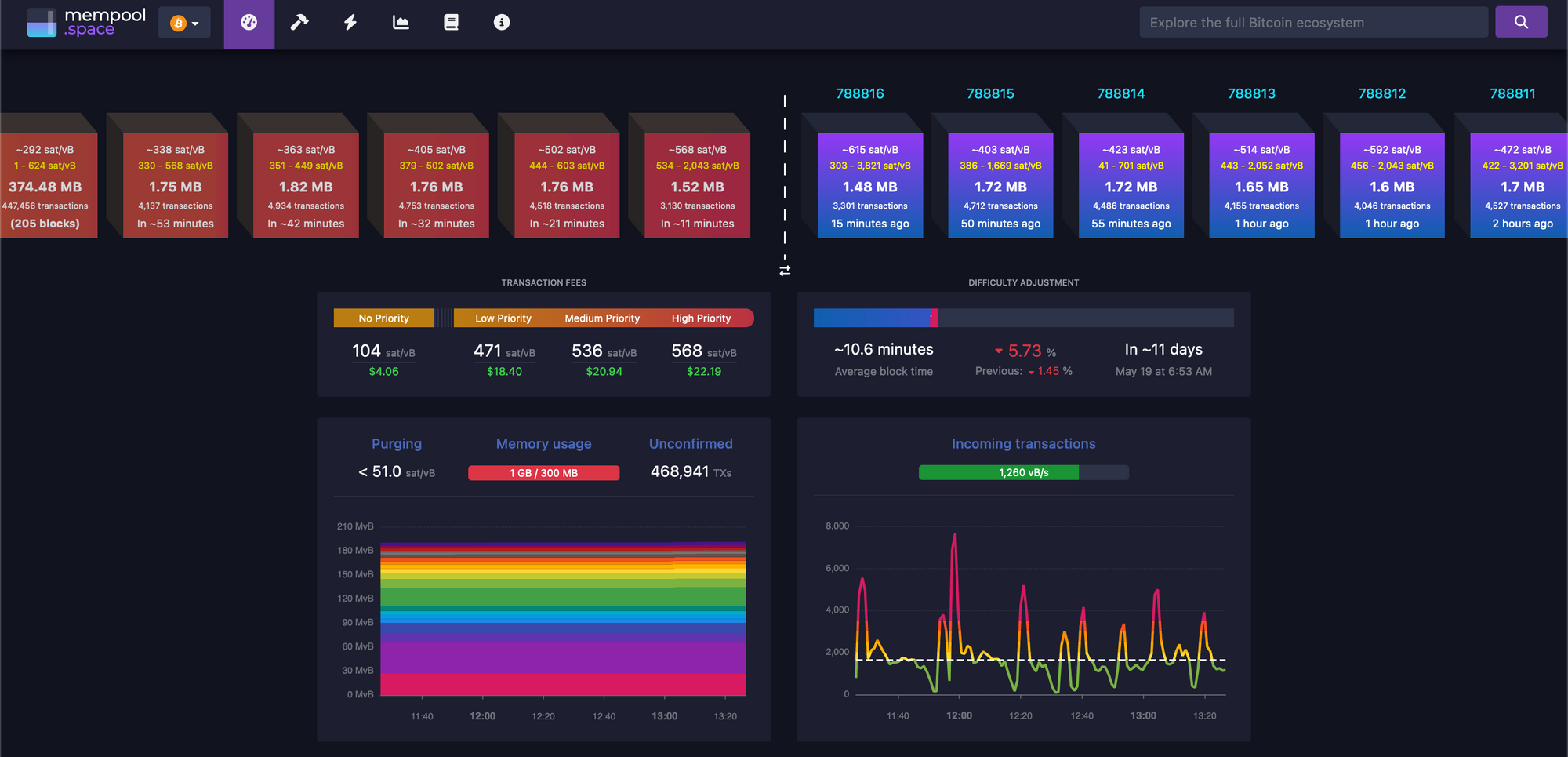
There must be a limit to how much data is transferred across the bitcoin network in order to keep the ability to run and use your own node accessible. A node is required to interact with the global bitcoin network - if you do not use your own node then you must trust someone else's node. If nodes become inaccessible to run then the network will centralize around the remaining entities that operate them - threatening the censorship resistance at the core of bitcoin's value prop. The bitcoin protocol uses three main mechanisms to keep node operation costs low - a fixed limit on the amount of data in each block, an automatic difficulty adjustment that regulates how many blocks are produced based on current mining hash rate, and a robust dynamic transaction fee market.
Bitcoin transaction fees limit network abuse by making usage expensive. There is a cost to every transaction, set by a dynamic free market based on demand for scarce block space. It is an incredibly robust way to prevent spam without relying on centralized entities that can be corrupted or pressured.
After the 2017 bitcoin fee spike we had six years of relative quiet to build tools that would be robust in a sustained high fee market. Fortunately our tools are significantly better now but many still need improvement. Most of the pain points we see today will be mitigated.
The reality is we were never going to be fully prepared - pressure is needed to show the pain points and provide strong incentives to mitigate them.
It will be incredibly interesting to watch how projects adapt under pressure. Optimistic we see great innovation here.
_If you are willing to wait for your transaction to confirm you can pay significantly lower fees. Learn best practices for reducing your fee burden here.
My guide for running and using your own bitcoin node can be found here._
If you found this post helpful support my work with bitcoin.

-
 @ eb0157af:77ab6c55
2025-05-27 05:01:20
@ eb0157af:77ab6c55
2025-05-27 05:01:20The exchange reveals the extent of the breach that occurred last December as federal authorities investigate the data leak.
Coinbase has disclosed that the personal data of 69,461 users was compromised during the breach in December 2024, according to documentation filed with the Maine Attorney General’s Office.
The disclosure comes after Coinbase announced last week that a group of hackers had demanded a $20 million ransom, threatening to publish the stolen data on the dark web. The attackers allegedly bribed overseas customer service agents to extract information from the company’s systems.
Coinbase had previously stated that the breach affected less than 1% of its user base, compromising KYC (Know Your Customer) data such as names, addresses, and email addresses. In a filing with the U.S. Securities and Exchange Commission (SEC), the company clarified that passwords, private keys, and user funds were not affected.
Following the reports, the SEC has reportedly opened an official investigation to verify whether Coinbase may have inflated user metrics ahead of its 2021 IPO. Separately, the Department of Justice is investigating the breach at Coinbase’s request, according to CEO Brian Armstrong.
Meanwhile, Coinbase has faced criticism for its delayed response to the data breach. Michael Arrington, founder of TechCrunch, stated that the stolen data could cause irreparable harm. In a post on X, Arrington wrote:
“The human cost, denominated in misery, is much larger than the $400m or so they think it will actually cost the company to reimburse people. The consequences to companies who do not adequately protect their customer information should include, without limitation, prison time for executives.”
Coinbase estimates the incident could cost between $180 million and $400 million in remediation expenses and customer reimbursements.
Arrington also condemned KYC laws as ineffective and dangerous, calling on both regulators and companies to better protect user data:
“Combining these KYC laws with corporate profit maximization and lax laws on penalties for hacks like these means these issues will continue to happen. Both governments and corporations need to step up to stop this. As I said, the cost can only be measured in human suffering.”
The post Coinbase: 69,461 users affected by December 2024 data breach appeared first on Atlas21.
-
 @ 7f6db517:a4931eda
2025-05-27 05:01:34
@ 7f6db517:a4931eda
2025-05-27 05:01:34
I often hear "bitcoin doesn't interest me, I'm not a finance person."
Ironically, the beauty of sound money is you don't have to be. In the current system you're expected to manage a diversified investment portfolio or pay someone to do it. Bitcoin will make that optional.
— ODELL (@ODELL) September 16, 2018
At first glance bitcoin often appears overwhelming to newcomers. It is incredibly easy to get bogged down in the details of how it works or different ways to use it. Enthusiasts, such as myself, often enjoy going down the deep rabbit hole of the potential of bitcoin, possible pitfalls and theoretical scenarios, power user techniques, and the developer ecosystem. If your first touch point with bitcoin is that type of content then it is only natural to be overwhelmed. While it is important that we have a thriving community of bitcoiners dedicated to these complicated tasks - the true beauty of bitcoin lies in its simplicity. Bitcoin is simply better money. It is the best money we have ever had.
Life is complicated. Life is hard. Life is full of responsibility and surprises. Bitcoin allows us to focus on our lives while relying on a money that is simple. A money that is not controlled by any individual, company, or government. A money that cannot be easily seized or blocked. A money that cannot be devalued at will by a handful of corrupt bureaucrat who live hundreds of miles from us. A money that can be easily saved and should increase in purchasing power over time without having to learn how to "build a diversified stock portfolio" or hire someone to do it for us.
Bitcoin enables all of us to focus on our lives - our friends and family - doing what we love with the short time we have on this earth. Time is scarce. Life is complicated. Bitcoin is the most simple aspect of our complicated lives. If we spend our scarce time working then we should be able to easily save that accrued value for future generations without watching the news or understanding complicated financial markets. Bitcoin makes this possible for anyone.
Yesterday was Mother's Day. Raising a human is complicated. It is hard, it requires immense personal responsibility, it requires critical thinking, but mothers figure it out, because it is worth it. Using and saving bitcoin is simple - simply install an app on your phone. Every mother can do it. Every person can do it.
Life is complicated. Life is beautiful. Bitcoin is simple.
If you found this post helpful support my work with bitcoin.

-
 @ 7f6db517:a4931eda
2025-05-27 05:01:33
@ 7f6db517:a4931eda
2025-05-27 05:01:33Will not live in a pod.
Will not eat the bugs.
Will not get the chip.
Will not get a blue check.
Will not use CBDCs.Live Free or Die.

Why did Elon buy twitter for $44 Billion? What value does he see in it besides the greater influence that undoubtedly comes with controlling one of the largest social platforms in the world? We do not need to speculate - he made his intentions incredibly clear in his first meeting with twitter employees after his takeover - WeChat of the West.
To those that do not appreciate freedom, the value prop is clear - WeChat is incredibly powerful and successful in China.
To those that do appreciate freedom, the concern is clear - WeChat has essentially become required to live in China, has surveillance and censorship integrated at its core, and if you are banned from the app your entire livelihood is at risk. Employment, housing, payments, travel, communication, and more become extremely difficult if WeChat censors determine you have acted out of line.
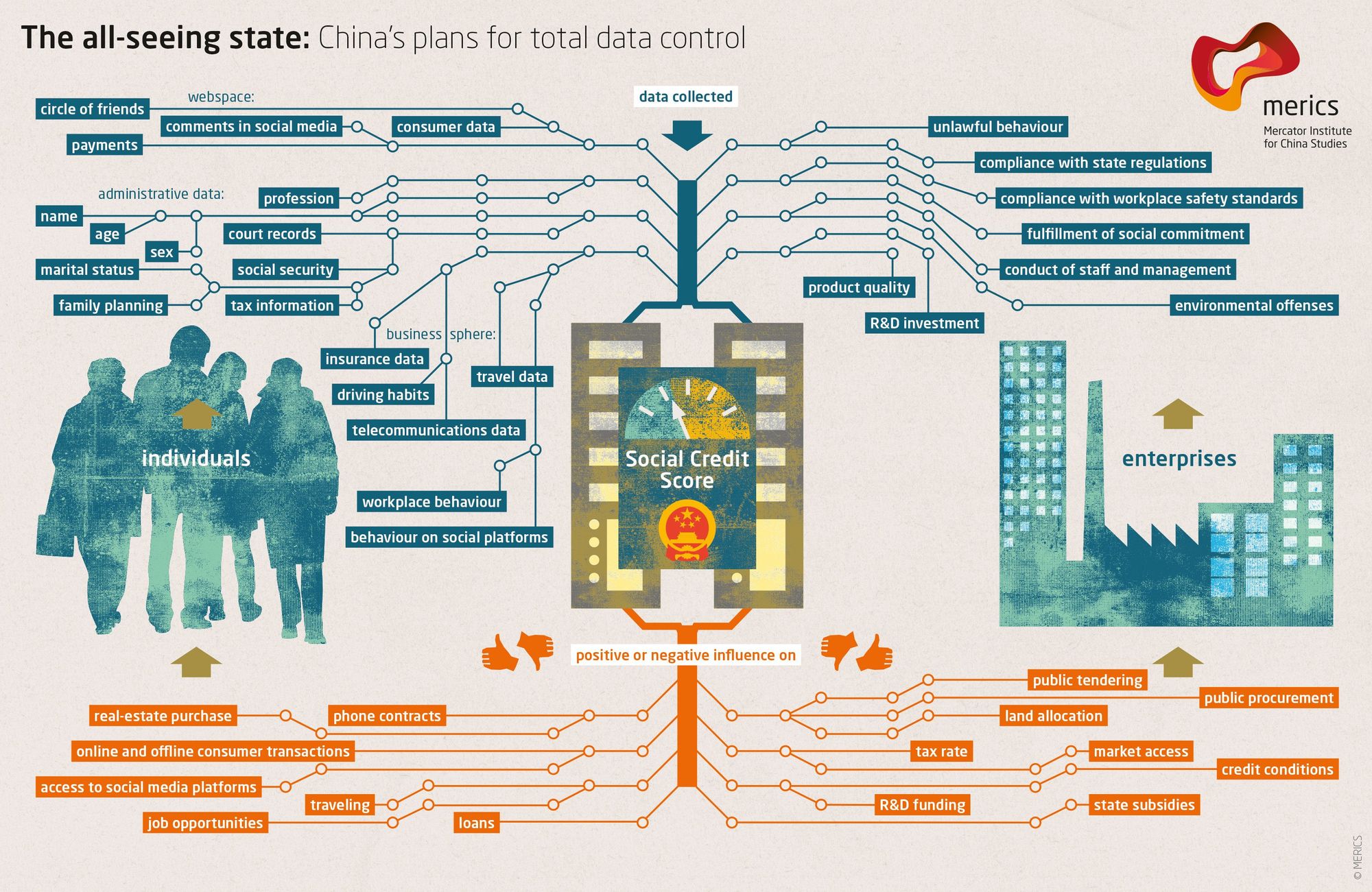
The blue check is the first step in Elon's plan to bring the chinese social credit score system to the west. Users who verify their identity are rewarded with more reach and better tools than those that do not. Verified users are the main product of Elon's twitter - an extensive database of individuals and complete control of the tools he will slowly get them to rely on - it is easier to monetize cattle than free men.
If you cannot resist the temptation of the blue check in its current form you have already lost - what comes next will be much darker. If you realize the need to resist - freedom tech provides us options.
If you found this post helpful support my work with bitcoin.

-
 @ c1e9ab3a:9cb56b43
2025-05-09 23:10:14
@ c1e9ab3a:9cb56b43
2025-05-09 23:10:14I. Historical Foundations of U.S. Monetary Architecture
The early monetary system of the United States was built atop inherited commodity money conventions from Europe’s maritime economies. Silver and gold coins—primarily Spanish pieces of eight, Dutch guilders, and other foreign specie—formed the basis of colonial commerce. These units were already integrated into international trade and piracy networks and functioned with natural compatibility across England, France, Spain, and Denmark. Lacking a centralized mint or formal currency, the U.S. adopted these forms de facto.
As security risks and the practical constraints of physical coinage mounted, banks emerged to warehouse specie and issue redeemable certificates. These certificates evolved into fiduciary media—claims on specie not actually in hand. Banks observed over time that substantial portions of reserves remained unclaimed for years. This enabled fractional reserve banking: issuing more claims than reserves held, so long as redemption demand stayed low. The practice was inherently unstable, prone to panics and bank runs, prompting eventual centralization through the formation of the Federal Reserve in 1913.
Following the Civil War and unstable reinstatements of gold convertibility, the U.S. sought global monetary stability. After World War II, the Bretton Woods system formalized the U.S. dollar as the global reserve currency. The dollar was nominally backed by gold, but most international dollars were held offshore and recycled into U.S. Treasuries. The Nixon Shock of 1971 eliminated the gold peg, converting the dollar into pure fiat. Yet offshore dollar demand remained, sustained by oil trade mandates and the unique role of Treasuries as global reserve assets.
II. The Structure of Fiduciary Media and Treasury Demand
Under this system, foreign trade surpluses with the U.S. generate excess dollars. These surplus dollars are parked in U.S. Treasuries, thereby recycling trade imbalances into U.S. fiscal liquidity. While technically loans to the U.S. government, these purchases act like interest-only transfers—governments receive yield, and the U.S. receives spendable liquidity without principal repayment due in the short term. Debt is perpetually rolled over, rarely extinguished.
This creates an illusion of global subsidy: U.S. deficits are financed via foreign capital inflows that, in practice, function more like financial tribute systems than conventional debt markets. The underlying asset—U.S. Treasury debt—functions as the base reserve asset of the dollar system, replacing gold in post-Bretton Woods monetary logic.
III. Emergence of Tether and the Parastatal Dollar
Tether (USDT), as a private issuer of dollar-denominated tokens, mimics key central bank behaviors while operating outside the regulatory perimeter. It mints tokens allegedly backed 1:1 by U.S. dollars or dollar-denominated securities (mostly Treasuries). These tokens circulate globally, often in jurisdictions with limited banking access, and increasingly serve as synthetic dollar substitutes.
If USDT gains dominance as the preferred medium of exchange—due to technological advantages, speed, programmability, or access—it displaces Federal Reserve Notes (FRNs) not through devaluation, but through functional obsolescence. Gresham’s Law inverts: good money (more liquid, programmable, globally transferable USDT) displaces bad (FRNs) even if both maintain a nominal 1:1 parity.
Over time, this preference translates to a systemic demand shift. Actors increasingly use Tether instead of FRNs, especially in global commerce, digital marketplaces, or decentralized finance. Tether tokens effectively become shadow base money.
IV. Interaction with Commercial Banking and Redemption Mechanics
Under traditional fractional reserve systems, commercial banks issue loans denominated in U.S. dollars, expanding the money supply. When borrowers repay loans, this destroys the created dollars and contracts monetary elasticity. If borrowers repay in USDT instead of FRNs:
- Banks receive a non-Fed liability (USDT).
- USDT is not recognized as reserve-eligible within the Federal Reserve System.
- Banks must either redeem USDT for FRNs, or demand par-value conversion from Tether to settle reserve requirements and balance their books.
This places redemption pressure on Tether and threatens its 1:1 peg under stress. If redemption latency, friction, or cost arises, USDT’s equivalence to FRNs is compromised. Conversely, if banks are permitted or compelled to hold USDT as reserve or regulatory capital, Tether becomes a de facto reserve issuer.
In this scenario, banks may begin demanding loans in USDT, mirroring borrower behavior. For this to occur sustainably, banks must secure Tether liquidity. This creates two options: - Purchase USDT from Tether or on the secondary market, collateralized by existing fiat. - Borrow USDT directly from Tether, using bank-issued debt as collateral.
The latter mirrors Federal Reserve discount window operations. Tether becomes a lender of first resort, providing monetary elasticity to the banking system by creating new tokens against promissory assets—exactly how central banks function.
V. Structural Consequences: Parallel Central Banking
If Tether begins lending to commercial banks, issuing tokens backed by bank notes or collateralized debt obligations: - Tether controls the expansion of broad money through credit issuance. - Its balance sheet mimics a central bank, with Treasuries and bank debt as assets and tokens as liabilities. - It intermediates between sovereign debt and global liquidity demand, replacing the Federal Reserve’s open market operations with its own issuance-redemption cycles.
Simultaneously, if Tether purchases U.S. Treasuries with FRNs received through token issuance, it: - Supplies the Treasury with new liquidity (via bond purchases). - Collects yield on government debt. - Issues a parallel form of U.S. dollars that never require redemption—an interest-only loan to the U.S. government from a non-sovereign entity.
In this context, Tether performs monetary functions of both a central bank and a sovereign wealth fund, without political accountability or regulatory transparency.
VI. Endgame: Institutional Inversion and Fed Redundancy
This paradigm represents an institutional inversion:
- The Federal Reserve becomes a legacy issuer.
- Tether becomes the operational base money provider in both retail and interbank contexts.
- Treasuries remain the foundational reserve asset, but access to them is mediated by a private intermediary.
- The dollar persists, but its issuer changes. The State becomes a fiscal agent of a decentralized financial ecosystem, not its monetary sovereign.
Unless the Federal Reserve reasserts control—either by absorbing Tether, outlawing its instruments, or integrating its tokens into the reserve framework—it risks becoming irrelevant in the daily function of money.
Tether, in this configuration, is no longer a derivative of the dollar—it is the dollar, just one level removed from sovereign control. The future of monetary sovereignty under such a regime is post-national and platform-mediated.
-
 @ cae03c48:2a7d6671
2025-05-26 22:00:48
@ cae03c48:2a7d6671
2025-05-26 22:00:48Bitcoin Magazine
Bitcoin Pizza Day: 15 Years Since 10,000 BTC Bought Two Pizzas and Changed EverythingOn May 22, 2010, Bitcoin became more than just an idea—it became real money. Laszlo Hanyecz, a developer and early contributor to Bitcoin’s codebase, posted a casual offer: “I’ll pay 10,000 bitcoins for a couple of pizzas.” Five days later, someone took him up on it. Two Papa John’s pizzas were delivered. A screenshot was posted. Bitcoin had entered the real world.
15 years ago, Laszlo Hanyecz spent 10,000 #bitcoin worth $30 on two Papa John's pizzas.
Today, 10,000 $BTC is worth over $1,100,000,000.
What a legend!
 pic.twitter.com/EbxQAsixhZ
pic.twitter.com/EbxQAsixhZ— Bitcoin Magazine (@BitcoinMagazine) May 22, 2025
That 10,000 Bitcoin, worth about $41 at the time, is now valued at over $1.1 billion. And with Bitcoin hitting a new all-time high of $111,999 on the 15th anniversary of the transaction, the story of the “Bitcoin Pizza” carries more weight than ever.
15 years ago, someone paid 10,000 #Bitcoin for 2 pizzas. That’s worth over $1,000,000,000 today!

It wasn’t just about the pizza. This was the moment Bitcoin proved itself as a functioning currency. Until then, it had lived mostly in theory and code—talked about by cryptographers and mined by hobbyists. Hanyecz’s post, and the trade that followed, transformed the idea into action. “This transaction made Bitcoin real in my eyes,” he said in a 2019 interview. “It wasn’t worth much at the time. I wouldn’t have spent $100 million on pizza, right? But if I hadn’t done that, maybe Bitcoin wouldn’t have become so popular.”
Over the summer of 2010, Hanyecz continued using Bitcoin to buy pizzas, eventually spending more than 79,000 BTC—now worth nearly $8.7 billion. While some have joked at his expense, the truth is this: without those early real-world transactions, Bitcoin might never have proven its use case. Hanyecz helped move Bitcoin from the fringe into functionality.
That legacy still shapes us today. Bitcoin Pizza Day has become a cultural milestone in the crypto world, with meetups, pizza parties, and educational events held globally each May 22. The day serves as a reminder of how far the technology has come—and the importance of everyday actions and the impact they have.
Smiles, joy, and shared moments, this is what today looked like.#Bitcoin Pizza Day at His Grace School was more than a visit. It was connection, care, and community. A heartfelt thank you to everyone who donated and supported #BitcoinGhana #BitcoinPizzaDay #BTC #Bitfiasi pic.twitter.com/xRMv1rpife
— Bitfiasi Initiative (@bitfiasi) May 22, 2025
Just this week, fast food chain Steak ‘n Shake began accepting Bitcoin via the Lightning Network, signaling a growing wave of mainstream adoption. What once felt experimental is now becoming part of everyday commerce.
Bitcoin Pizza Day is about recognition. One simple transaction proved that Bitcoin could work—and 15 years later, the world is still building on that first bite.
This post Bitcoin Pizza Day: 15 Years Since 10,000 BTC Bought Two Pizzas and Changed Everything first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ 21335073:a244b1ad
2025-05-09 13:56:57
@ 21335073:a244b1ad
2025-05-09 13:56:57Someone asked for my thoughts, so I’ll share them thoughtfully. I’m not here to dictate how to promote Nostr—I’m still learning about it myself. While I’m not new to Nostr, freedom tech is a newer space for me. I’m skilled at advocating for topics I deeply understand, but freedom tech isn’t my expertise, so take my words with a grain of salt. Nothing I say is set in stone.
Those who need Nostr the most are the ones most vulnerable to censorship on other platforms right now. Reaching them requires real-time awareness of global issues and the dynamic relationships between governments and tech providers, which can shift suddenly. Effective Nostr promoters must grasp this and adapt quickly.
The best messengers are people from or closely tied to these at-risk regions—those who truly understand the local political and cultural dynamics. They can connect with those in need when tensions rise. Ideal promoters are rational, trustworthy, passionate about Nostr, but above all, dedicated to amplifying people’s voices when it matters most.
Forget influencers, corporate-backed figures, or traditional online PR—it comes off as inauthentic, corny, desperate and forced. Nostr’s promotion should be grassroots and organic, driven by a few passionate individuals who believe in Nostr and the communities they serve.
The idea that “people won’t join Nostr due to lack of reach” is nonsense. Everyone knows X’s “reach” is mostly with bots. If humans want real conversations, Nostr is the place. X is great for propaganda, but Nostr is for the authentic voices of the people.
Those spreading Nostr must be so passionate they’re willing to onboard others, which is time-consuming but rewarding for the right person. They’ll need to make Nostr and onboarding a core part of who they are. I see no issue with that level of dedication. I’ve been known to get that way myself at times. It’s fun for some folks.
With love, I suggest not adding Bitcoin promotion with Nostr outreach. Zaps already integrate that element naturally. (Still promote within the Bitcoin ecosystem, but this is about reaching vulnerable voices who needed Nostr yesterday.)
To promote Nostr, forget conventional strategies. “Influencers” aren’t the answer. “Influencers” are not the future. A trusted local community member has real influence—reach them. Connect with people seeking Nostr’s benefits but lacking the technical language to express it. This means some in the Nostr community might need to step outside of the Bitcoin bubble, which is uncomfortable but necessary. Thank you in advance to those who are willing to do that.
I don’t know who is paid to promote Nostr, if anyone. This piece isn’t shade. But it’s exhausting to see innocent voices globally silenced on corporate platforms like X while Nostr exists. Last night, I wondered: how many more voices must be censored before the Nostr community gets uncomfortable and thinks creatively to reach the vulnerable?
A warning: the global need for censorship-resistant social media is undeniable. If Nostr doesn’t make itself known, something else will fill that void. Let’s start this conversation.
-
 @ 7f6db517:a4931eda
2025-05-27 05:01:33
@ 7f6db517:a4931eda
2025-05-27 05:01:33
Nostr is an open communication protocol that can be used to send messages across a distributed set of relays in a censorship resistant and robust way.
If you missed my nostr introduction post you can find it here. My nostr account can be found here.
We are nearly at the point that if something interesting is posted on a centralized social platform it will usually be posted by someone to nostr.
We are nearly at the point that if something interesting is posted exclusively to nostr it is cross posted by someone to various centralized social platforms.
We are nearly at the point that you can recommend a cross platform app that users can install and easily onboard without additional guides or resources.
As companies continue to build walls around their centralized platforms nostr posts will be the easiest to cross reference and verify - as companies continue to censor their users nostr is the best censorship resistant alternative - gradually then suddenly nostr will become the standard. 🫡
Current Nostr Stats
If you found this post helpful support my work with bitcoin.

-
 @ 7f6db517:a4931eda
2025-05-27 05:01:33
@ 7f6db517:a4931eda
2025-05-27 05:01:33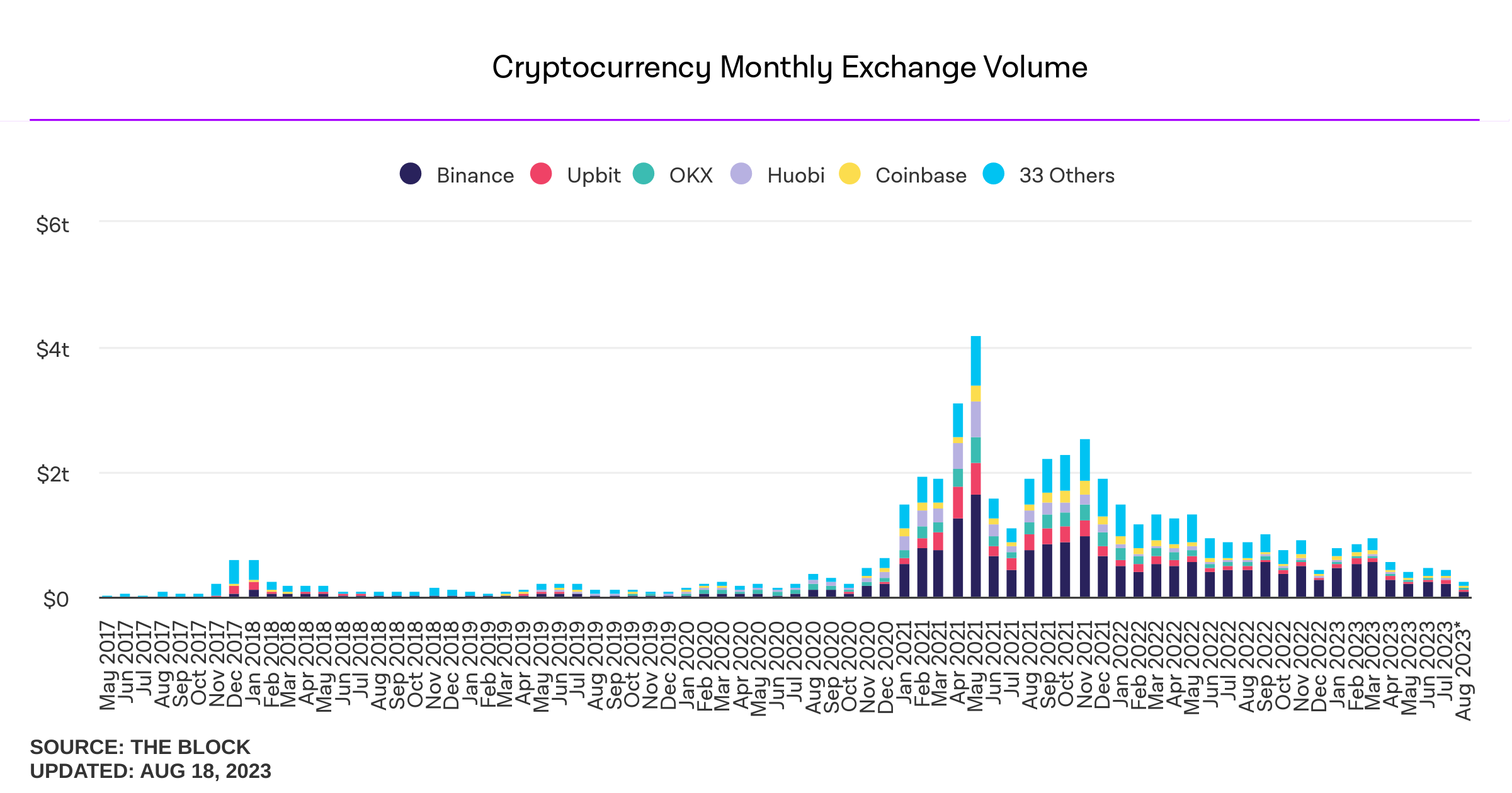
Influencers would have you believe there is an ongoing binance bank run but bitcoin wallet data says otherwise.
- binance wallets are near all time highs
- bitfinex wallets are also trending up
- gemini and coinbase are being hit with massive withdrawals thoughYou should not trust custodians, they can rug you without warning. It is incredibly important you learn how to hold bitcoin yourself, but also consider not blindly trusting influencers with a ref link to shill you.
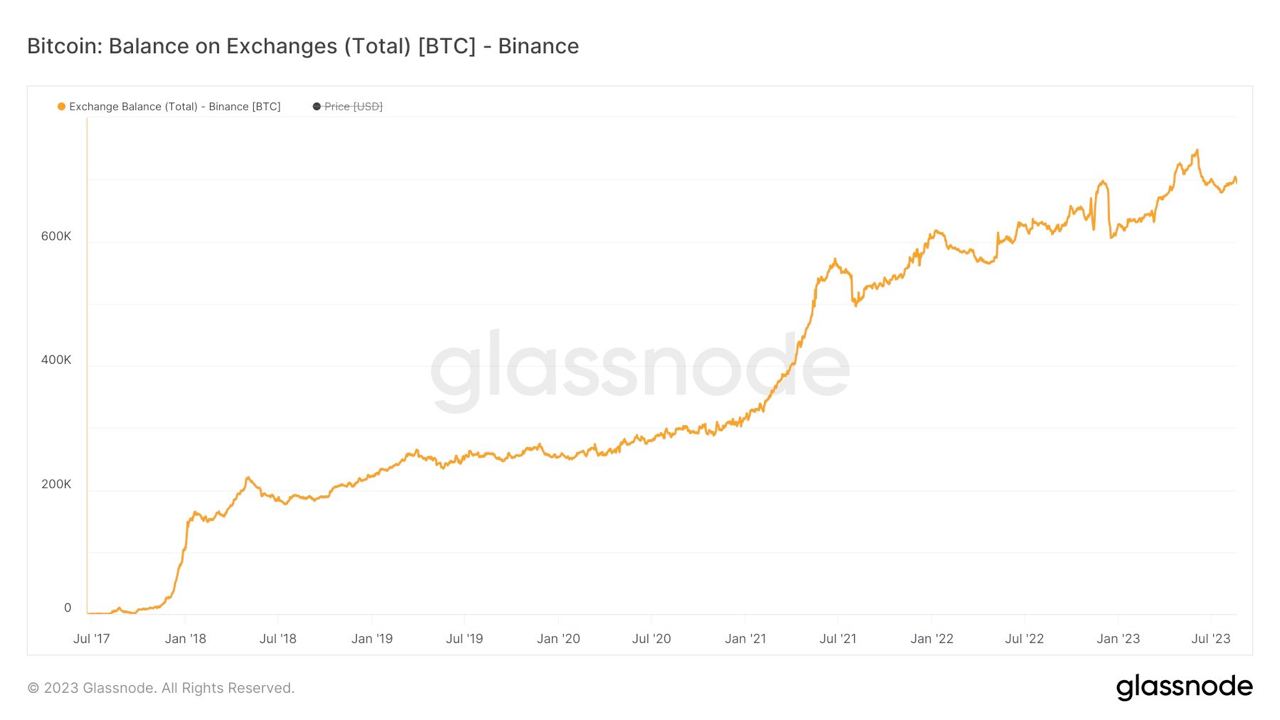
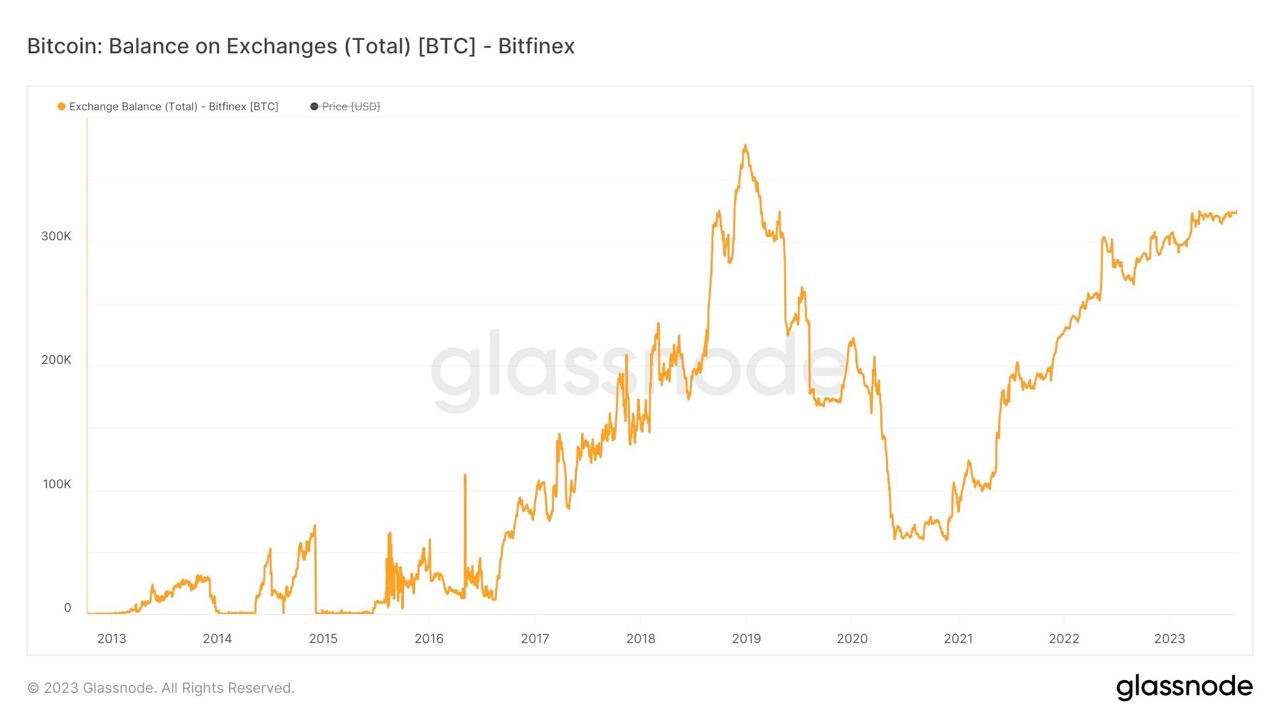
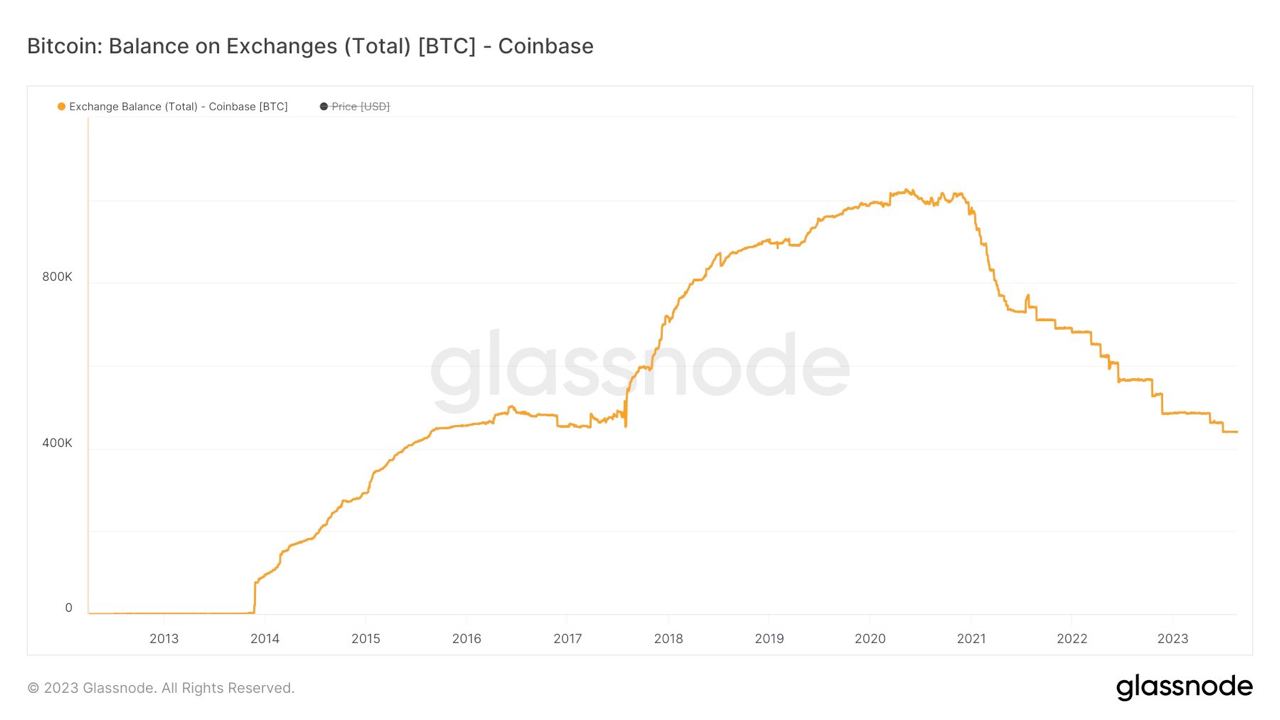

If you found this post helpful support my work with bitcoin.

-
 @ c9badfea:610f861a
2025-05-26 21:30:33
@ c9badfea:610f861a
2025-05-26 21:30:33- Install Loop Habit Tracker (it's free and open source)
- Launch the app, tap ➡️
- Tap ⁝, select Settings, scroll down and tap Customize Notifications
- Enable Show Notifications
- Return to the main screen
- Tap + to add a habit
- Choose Yes Or No for simple yes/no questions (e.g. Did you wake up early?)
- Choose Measurable for questions where a quantity is expected (e.g. How many pages did you read?)
- Assign a Name (e.g. Waking up early)
- Enter a Question (e.g. Did you wake up early?)
- Define the Frequency (e.g. Every Day)
- Schedule a Reminder (e.g. 08:00 and Any Day Of The Week)
- Include a Note if needed
- Hit Save to create the habit
- Start tracking your habits!
ℹ️ To categorize habits, use colors (e.g. blue for morning, orange for afternoon) or title prefixes (e.g. "Morning - Waking Up Early" and "Afternoon - Workout")
-
 @ 26769dac:498e333b
2025-05-26 18:34:14
@ 26769dac:498e333b
2025-05-26 18:34:14My life is my way Home\ My death is my arrival
I can't wait to be Home\ And so I love life
I can't wait to be Home\ And so I want to live to the fullest
For there are no shortcuts
Many people die\ And never make it Home
They will have to wait\ For another chance to die
Another chance to live fully\ And die totally
I'm so thankful to be alive\ I'm on my way Home
I'm so thankful to be alive\ To have another chance to die
Every day I take a step\ In the direction of my death\ I do not postpone it
Every day I take a step\ In the direction of my truth\ I do not avoid it
It is who I am, always have been\ And always will be
It lies beyond that door\ That keeps everything in check
Where only can go through\ Which is forever true
-
 @ 7f6db517:a4931eda
2025-05-27 05:01:33
@ 7f6db517:a4931eda
2025-05-27 05:01:33
For years American bitcoin miners have argued for more efficient and free energy markets. It benefits everyone if our energy infrastructure is as efficient and robust as possible. Unfortunately, broken incentives have led to increased regulation throughout the sector, incentivizing less efficient energy sources such as solar and wind at the detriment of more efficient alternatives.
The result has been less reliable energy infrastructure for all Americans and increased energy costs across the board. This naturally has a direct impact on bitcoin miners: increased energy costs make them less competitive globally.
Bitcoin mining represents a global energy market that does not require permission to participate. Anyone can plug a mining computer into power and internet to get paid the current dynamic market price for their work in bitcoin. Using cellphone or satellite internet, these mines can be located anywhere in the world, sourcing the cheapest power available.
Absent of regulation, bitcoin mining naturally incentivizes the build out of highly efficient and robust energy infrastructure. Unfortunately that world does not exist and burdensome regulations remain the biggest threat for US based mining businesses. Jurisdictional arbitrage gives miners the option of moving to a friendlier country but that naturally comes with its own costs.
Enter AI. With the rapid development and release of AI tools comes the requirement of running massive datacenters for their models. Major tech companies are scrambling to secure machines, rack space, and cheap energy to run full suites of AI enabled tools and services. The most valuable and powerful tech companies in America have stumbled into an accidental alliance with bitcoin miners: THE NEED FOR CHEAP AND RELIABLE ENERGY.
Our government is corrupt. Money talks. These companies will push for energy freedom and it will greatly benefit us all.
Microsoft Cloud hiring to "implement global small modular reactor and microreactor" strategy to power data centers: https://www.datacenterdynamics.com/en/news/microsoft-cloud-hiring-to-implement-global-small-modular-reactor-and-microreactor-strategy-to-power-data-centers/
If you found this post helpful support my work with bitcoin.

-
 @ d61f3bc5:0da6ef4a
2025-05-05 15:26:08
@ d61f3bc5:0da6ef4a
2025-05-05 15:26:08I remember the first gathering of Nostr devs two years ago in Costa Rica. We were all psyched because Nostr appeared to solve the problem of self-sovereign online identity and decentralized publishing. The protocol seemed well-suited for textual content, but it wasn't really designed to handle binary files, like images or video.
The Problem
When I publish a note that contains an image link, the note itself is resilient thanks to Nostr, but if the hosting service disappears or takes my image down, my note will be broken forever. We need a way to publish binary data without relying on a single hosting provider.
We were discussing how there really was no reliable solution to this problem even outside of Nostr. Peer-to-peer attempts like IPFS simply didn't work; they were hopelessly slow and unreliable in practice. Torrents worked for popular files like movies, but couldn't be relied on for general file hosting.
Awesome Blossom
A year later, I attended the Sovereign Engineering demo day in Madeira, organized by Pablo and Gigi. Many projects were presented over a three hour demo session that day, but one really stood out for me.
Introduced by hzrd149 and Stu Bowman, Blossom blew my mind because it showed how we can solve complex problems easily by simply relying on the fact that Nostr exists. Having an open user directory, with the corresponding social graph and web of trust is an incredible building block.
Since we can easily look up any user on Nostr and read their profile metadata, we can just get them to simply tell us where their files are stored. This, combined with hash-based addressing (borrowed from IPFS), is all we need to solve our problem.
How Blossom Works
The Blossom protocol (Blobs Stored Simply on Mediaservers) is formally defined in a series of BUDs (Blossom Upgrade Documents). Yes, Blossom is the most well-branded protocol in the history of protocols. Feel free to refer to the spec for details, but I will provide a high level explanation here.
The main idea behind Blossom can be summarized in three points:
- Users specify which media server(s) they use via their public Blossom settings published on Nostr;
- All files are uniquely addressable via hashes;
- If an app fails to load a file from the original URL, it simply goes to get it from the server(s) specified in the user's Blossom settings.
Just like Nostr itself, the Blossom protocol is dead-simple and it works!
Let's use this image as an example:
 If you look at the URL for this image, you will notice that it looks like this:
If you look at the URL for this image, you will notice that it looks like this:blossom.primal.net/c1aa63f983a44185d039092912bfb7f33adcf63ed3cae371ebe6905da5f688d0.jpgAll Blossom URLs follow this format:
[server]/[file-hash].[extension]The file hash is important because it uniquely identifies the file in question. Apps can use it to verify that the file they received is exactly the file they requested. It also gives us the ability to reliably get the same file from a different server.
Nostr users declare which media server(s) they use by publishing their Blossom settings. If I store my files on Server A, and they get removed, I can simply upload them to Server B, update my public Blossom settings, and all Blossom-capable apps will be able to find them at the new location. All my existing notes will continue to display media content without any issues.
Blossom Mirroring
Let's face it, re-uploading files to another server after they got removed from the original server is not the best user experience. Most people wouldn't have the backups of all the files, and/or the desire to do this work.
This is where Blossom's mirroring feature comes handy. In addition to the primary media server, a Blossom user can set one one or more mirror servers. Under this setup, every time a file is uploaded to the primary server the Nostr app issues a mirror request to the primary server, directing it to copy the file to all the specified mirrors. This way there is always a copy of all content on multiple servers and in case the primary becomes unavailable, Blossom-capable apps will automatically start loading from the mirror.
Mirrors are really easy to setup (you can do it in two clicks in Primal) and this arrangement ensures robust media handling without any central points of failure. Note that you can use professional media hosting services side by side with self-hosted backup servers that anyone can run at home.
Using Blossom Within Primal
Blossom is natively integrated into the entire Primal stack and enabled by default. If you are using Primal 2.2 or later, you don't need to do anything to enable Blossom, all your media uploads are blossoming already.
To enhance user privacy, all Primal apps use the "/media" endpoint per BUD-05, which strips all metadata from uploaded files before they are saved and optionally mirrored to other Blossom servers, per user settings. You can use any Blossom server as your primary media server in Primal, as well as setup any number of mirrors:
 ## Conclusion
## ConclusionFor such a simple protocol, Blossom gives us three major benefits:
- Verifiable authenticity. All Nostr notes are always signed by the note author. With Blossom, the signed note includes a unique hash for each referenced media file, making it impossible to falsify a media file and maliciously ascribe it to the note author.
- File hosting redundancy. Having multiple live copies of referenced media files (via Blossom mirroring) greatly increases the resiliency of media content published on Nostr.
- Censorship resistance. Blossom enables us to seamlessly switch media hosting providers in case of censorship.
Thanks for reading; and enjoy! 🌸
-
 @ 2183e947:f497b975
2025-05-01 22:33:48
@ 2183e947:f497b975
2025-05-01 22:33:48Most darknet markets (DNMs) are designed poorly in the following ways:
1. Hosting
Most DNMs use a model whereby merchants fill out a form to create their listings, and the data they submit then gets hosted on the DNM's servers. In scenarios where a "legal" website would be forced to censor that content (e.g. a DMCA takedown order), DNMs, of course, do not obey. This can lead to authorities trying to find the DNM's servers to take enforcement actions against them. This design creates a single point of failure.
A better design is to outsource hosting to third parties. Let merchants host their listings on nostr relays, not on the DNM's server. The DNM should only be designed as an open source interface for exploring listings hosted elsewhere, that way takedown orders end up with the people who actually host the listings, i.e. with nostr relays, and not with the DNM itself. And if a nostr relay DOES go down due to enforcement action, it does not significantly affect the DNM -- they'll just stop querying for listings from that relay in their next software update, because that relay doesn't work anymore, and only query for listings from relays that still work.
2. Moderation
Most DNMs have employees who curate the listings on the DNM. For example, they approve/deny listings depending on whether they fit the content policies of the website. Some DNMs are only for drugs, others are only for firearms. The problem is, to approve a criminal listing is, in the eyes of law enforcement, an act of conspiracy. Consequently, they don't just go after the merchant who made the listing but the moderators who approved it, and since the moderators typically act under the direction of the DNM, this means the police go after the DNM itself.
A better design is to outsource moderation to third parties. Let anyone call themselves a moderator and create lists of approved goods and services. Merchants can pay the most popular third party moderators to add their products to their lists. The DNM itself just lets its users pick which moderators to use, such that the user's choice -- and not a choice by the DNM -- determines what goods and services the user sees in the interface.
That way, the police go after the moderators and merchants rather than the DNM itself, which is basically just a web browser: it doesn't host anything or approve of any content, it just shows what its users tell it to show. And if a popular moderator gets arrested, his list will still work for a while, but will gradually get more and more outdated, leading someone else to eventually become the new most popular moderator, and a natural transition can occur.
3. Escrow
Most DNMs offer an escrow solution whereby users do not pay merchants directly. Rather, during the Checkout process, they put their money in escrow, and request the DNM to release it to the merchant when the product arrives, otherwise they initiate a dispute. Most DNMs consider escrow necessary because DNM users and merchants do not trust one another; users don't want to pay for a product first and then discover that the merchant never ships it, and merchants don't want to ship a product first and then discover that the user never pays for it.
The problem is, running an escrow solution for criminals is almost certain to get you accused of conspiracy, money laundering, and unlicensed money transmission, so the police are likely to shut down any DNM that does this. A better design is to oursource escrow to third parties. Let anyone call themselves an escrow, and let moderators approve escrows just like they approve listings. A merchant or user who doesn't trust the escrows chosen by a given moderator can just pick a different moderator. That way, the police go after the third party escrows rather than the DNM itself, which never touches user funds.
4. Consequences
Designing a DNM along these principles has an interesting consequence: the DNM is no longer anything but an interface, a glorified web browser. It doesn't host any content, approve any listings, or touch any money. It doesn't even really need a server -- it can just be an HTML file that users open up on their computer or smart phone. For two reasons, such a program is hard to take down:
First, it is hard for the police to justify going after the DNM, since there are no charges to bring. Its maintainers aren't doing anything illegal, no more than Firefox does anything illegal by maintaining a web browser that some people use to browse illegal content. What the user displays in the app is up to them, not to the code maintainers. Second, if the police decided to go after the DNM anyway, they still couldn't take it down because it's just an HTML file -- the maintainers do not even need to run a server to host the file, because users can share it with one another, eliminating all single points of failure.
Another consequence of this design is this: most of the listings will probably be legal, because there is more demand for legal goods and services than illegal ones. Users who want to find illegal goods would pick moderators who only approve those listings, but everyone else would use "legal" moderators, and the app would not, at first glance, look much like a DNM, just a marketplace for legal goods and services. To find the illegal stuff that lurks among the abundant legal stuff, you'd probably have to filter for it via your selection of moderators, making it seem like the "default" mode is legal.
5. Conclusion
I think this DNM model is far better than the designs that prevail today. It is easier to maintain, harder to take down, and pushes the "hard parts" to the edges, so that the DNM is not significantly affected even if a major merchant, moderator, or escrow gets arrested. I hope it comes to fruition.
-
 @ bf47c19e:c3d2573b
2025-05-26 16:56:52
@ bf47c19e:c3d2573b
2025-05-26 16:56:52Dragi Bitcoineri,
Kako se bliži treći mesec izostanka ličnog dohotka na Fakultetu dramskih umetnosti u Beogradu, a dosadašnji vidovi podrške ne mogu da pokriju sve profesore, neophodno je da preduzmemo dalje korake kako ne bi više ispaštali profesori zbog svoje otvorene podrške studentima u borbi za pravednije društvo.
Možda nekad, kad se spolja gleda, deluje kao da se ništa ne dešava na fakultetima ali u našoj zajednici konstantno vri. Borbu sa studentima osećamo kao svoju moralnu i građansku dužnost, a namera nam je da istrajemo na tom putu ka instuitucionalnoj odgovornosti, slobodi i pravdi.
Doniraj BTC! Sve donacije idu u Bitcoin novčanik studenata u blokadi FDU! Hvala unapred ❤️

-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ da8b7de1:c0164aee
2025-05-26 15:15:56
@ da8b7de1:c0164aee
2025-05-26 15:15:56Technológiai fejlemények
Az Egyesült Államokban Donald Trump négy végrehajtási rendeletet írt alá, amelyek célja a nukleáris ipar gyors fejlesztése és az ország nukleáris kapacitásának 2050-ig történő megnégyszerezése. Ezek a rendeletek támogatják az új generációs reaktorok – különösen a kisméretű moduláris reaktorok (SMR-ek) és mikroreaktorok – gyorsabb engedélyezését és telepítését, beleértve katonai létesítményeket és mesterséges intelligenciát használó adatközpontokat is. Továbbá lehetővé teszik a használt nukleáris üzemanyag újrahasznosítását, valamint ösztönzik a HALEU (magas tisztaságú, alacsony dúsítású urán) hazai előállítását, ezzel erősítve az amerikai nukleáris ellátási láncot.
Források:
- world-nuclear-news.org
- reuters.com
- bloomberg.comIpari fejlemények
Tajvanban augusztus 23-ára tűzték ki a Maanshan-2 atomerőmű újraindításáról szóló népszavazást. Az erőművet május közepén állították le a „nukleárismentes Tajvan” program részeként, azonban az ellenzék kezdeményezésére a lakosság dönthet az újraindításról. Az USA-ban a frissen aláírt végrehajtási rendeletek egyszerűsítik az engedélyezési folyamatokat, csökkentik a szabályozási terheket, és ösztönzik a magánbefektetéseket, ami a hazai uránbányászat és feldolgozás fellendülését eredményezheti.
Források:
- taipeitimes.com
- world-nuclear-news.orgPénzügyi hatások
A pénzügyi piacokon a nukleáris szektor részvényei jelentős emelkedést mutattak a Trump-féle rendeletek bejelentése után. Az Uranium Energy részvényei 11%-kal, az Oklo Inc. papírjai 16%-kal, a Global X Uranium ETF 9%-kal erősödtek. A növekedés hátterében a szabályozási könnyítések mellett az AI adatközpontok növekvő energiaigénye áll, amelyre a nagy technológiai cégek egyre inkább a nukleáris energiát tartják a legjobb megoldásnak. A kormányzati támogatás és a technológiai vállalatok befektetései új lendületet adhatnak a nukleáris iparnak, amely évek óta küzd a gazdasági és társadalmi kihívásokkal.
Források:
- bloomberg.com
- finance.yahoo.com
- reuters.com -
 @ 7f6db517:a4931eda
2025-05-27 05:01:32
@ 7f6db517:a4931eda
2025-05-27 05:01:32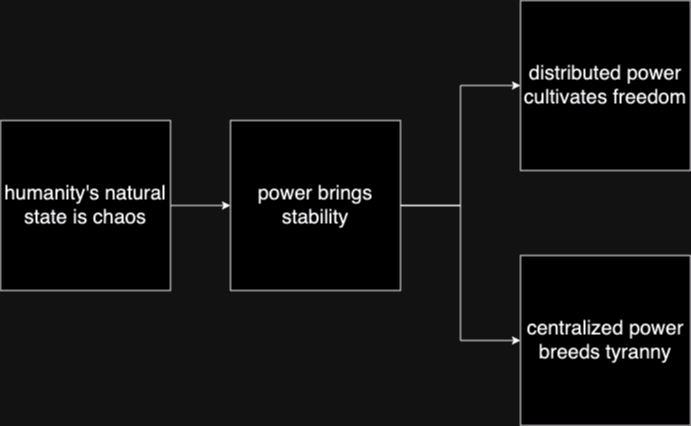
Humanity's Natural State Is Chaos
Without order there is chaos. Humans competing with each other for scarce resources naturally leads to conflict until one group achieves significant power and instates a "monopoly on violence."Power Brings Stability
Power has always been the key means to achieve stability in societies. Centralized power can be incredibly effective in addressing issues such as crime, poverty, and social unrest efficiently. Unfortunately this power is often abused and corrupted.Centralized Power Breeds Tyranny
Centralized power often leads to tyrannical rule. When a select few individuals hold control over a society, they tend to become corrupted. Centralized power structures often lack accountability and transparency, and rely too heavily on trust.Distributed Power Cultivates Freedom
New technology that empowers individuals provide us the ability to rebuild societies from the bottom up. Strong individuals that can defend and provide for themselves will help build strong local communities on a similar foundation. The result is power being distributed throughout society rather than held by a select few.In the short term, relying on trust and centralized power is an easy answer to mitigating chaos, but freedom tech tools provide us the ability to build on top of much stronger distributed foundations that provide stability while also cultivating individual freedom.
The solution starts with us. Empower yourself. Empower others. A grassroots freedom tech movement scaling one person at a time.
If you found this post helpful support my work with bitcoin.

-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ 7f6db517:a4931eda
2025-05-27 04:01:32
@ 7f6db517:a4931eda
2025-05-27 04:01:32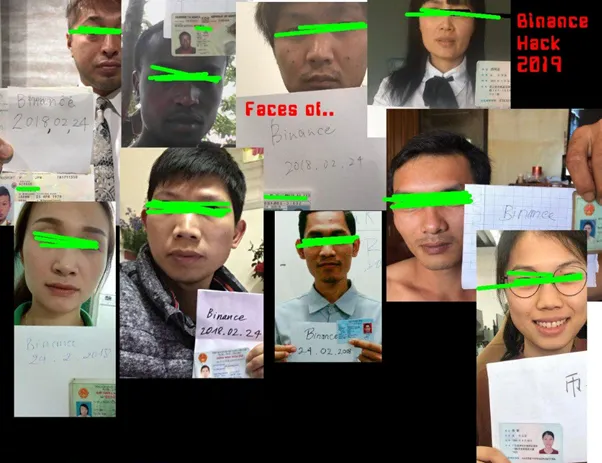
What is KYC/AML?
- The acronym stands for Know Your Customer / Anti Money Laundering.
- In practice it stands for the surveillance measures companies are often compelled to take against their customers by financial regulators.
- Methods differ but often include: Passport Scans, Driver License Uploads, Social Security Numbers, Home Address, Phone Number, Face Scans.
- Bitcoin companies will also store all withdrawal and deposit addresses which can then be used to track bitcoin transactions on the bitcoin block chain.
- This data is then stored and shared. Regulations often require companies to hold this information for a set number of years but in practice users should assume this data will be held indefinitely. Data is often stored insecurely, which results in frequent hacks and leaks.
- KYC/AML data collection puts all honest users at risk of theft, extortion, and persecution while being ineffective at stopping crime. Criminals often use counterfeit, bought, or stolen credentials to get around the requirements. Criminals can buy "verified" accounts for as little as $200. Furthermore, billions of people are excluded from financial services as a result of KYC/AML requirements.
During the early days of bitcoin most services did not require this sensitive user data, but as adoption increased so did the surveillance measures. At this point, most large bitcoin companies are collecting and storing massive lists of bitcoiners, our sensitive personal information, and our transaction history.
Lists of Bitcoiners
KYC/AML policies are a direct attack on bitcoiners. Lists of bitcoiners and our transaction history will inevitably be used against us.
Once you are on a list with your bitcoin transaction history that record will always exist. Generally speaking, tracking bitcoin is based on probability analysis of ownership change. Surveillance firms use various heuristics to determine if you are sending bitcoin to yourself or if ownership is actually changing hands. You can obtain better privacy going forward by using collaborative transactions such as coinjoin to break this probability analysis.
Fortunately, you can buy bitcoin without providing intimate personal information. Tools such as peach, hodlhodl, robosats, azteco and bisq help; mining is also a solid option: anyone can plug a miner into power and internet and earn bitcoin by mining privately.
You can also earn bitcoin by providing goods and/or services that can be purchased with bitcoin. Long term, circular economies will mitigate this threat: most people will not buy bitcoin - they will earn bitcoin - most people will not sell bitcoin - they will spend bitcoin.
There is no such thing as KYC or No KYC bitcoin, there are bitcoiners on lists and those that are not on lists.
If you found this post helpful support my work with bitcoin.

-
 @ 21335073:a244b1ad
2025-03-18 20:47:50
@ 21335073:a244b1ad
2025-03-18 20:47:50Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ 1f956aec:768866bd
2025-05-26 15:06:38
@ 1f956aec:768866bd
2025-05-26 15:06:38== January 17 2025
Out From Underneath | Prism Shores
crazy arms | pigeon pit
Humanhood | The Weather Station
== february 07 2025
Wish Defense | FACS
Sayan - Savoie | Maria Teriaeva
Nowhere Near Today | Midding
== february 14 2025
Phonetics On and On | Horsegirl
== february 21 2025
Finding Our Balance | Tsoh Tso
Machine Starts To Sing | Porridge Radio
Armageddon In A Summer Dress | Sunny Wa
== february 28 2025
you, infinite | you, infinite
On Being | Max Cooper
Billboard Heart | Deep Sea Diver
== March 21 2025
Watermelon/Peacock | Exploding Flowers
Warlord of the Weejuns | Goya Gumbani
== March 28 2025
Little Death Wishes | CocoRosie
Forever is a Feeling | Lucy Dacus
Evenfall | Sam Akpro
== April 4 2025
Tripla | Miki Berenyi Trio
Adagio | Σtella
The Fork | Oscar Jerome
== April 18 2025
Send A Prayer My Way | Julien Baker & TORRES
Superheaven | Superheaven
Thee Black Boltz | Tunde Adebimpe
from brooklyvegan
== April 25 2025
Face Down In The Garden |Tennis
Under Tangled Silence | Djrum
Viagr Aboys |Viagra Boys
Blurring Time | Bells Larsen
== May 2 2025
Time is Not Yours | Say Sue Me 세이수미
If You Asked For A Picture | Blondshell
== May 16 2025
Wield Your Hope Like A Weapon | Soot Sprite
Transmission 96 | Liftin Spirits & DJ Persuasion
Menedék | TÖRZS
== May 28 2025
Forefowk, Mind Me | Quinie
Silver Tears | SILVER TEARS
-
 @ a296b972:e5a7a2e8
2025-05-26 12:42:46
@ a296b972:e5a7a2e8
2025-05-26 12:42:46Zahlreiche Anzeichen deuten darauf hin, dass die Zeit zu Ende geht, in der Europa, vor allem Deutschland, unter den schützenden Flügeln des US-Adlers bleiben kann. Die europäischen Küken sind noch nicht flügge, werden aber jetzt aus dem wohligen Nest geworfen und in die Freiheit entlassen. Ängstlich schlagen sie mit den Flügeln, doch das Fliegen will nicht so recht gelingen.
Angstbenommenheit, Inkompetenz und blinder Aktionismus erzeugen so staatsmännisch klingende Sprüche wie die, dass Deutschland zur stärksten Kraft in Europa werden soll. Hieran erkennt man die pubertäre Unreife, weil es kein Bewusstsein dafür gibt, was diese Aussage im Ausland unter Umständen bewirken kann. Man kann sich vorstellen, dass so etwas vor allem in der Bevölkerung des jahrelangen Erzfeindes Frankreich ein ungutes Gefühl erwecken könnte.
Ebenso bei den Briten, die möglicherweise ebenfalls nicht vor lauter Begeisterung vollends aus dem Häuschen sein werden.
Die USA und Russland beobachten sehr genau, was in Deutschland vorgeht, wobei die Aussage des zukünftigen Ex-Bundeskanzlers in Russland möglicherweise nur ein süffisantes Lächeln erzeugt, so, wie wenn ein Yorkshire-Terrier einen Bull-Dog ankläffen würde.
Deutschland scheint nicht den geringsten Schimmer davon zu haben, mit wem es sich anlegt.
Wenn für die Russen der "unschöne Besuch" der Deutschen in Russland mit rund 27 Millionen Toten an Bedeutung verloren hätte, würden die Paraden zum Sieg über den Faschismus nicht nach wie vor so groß gefeiert werden. Wenn die deutschen Regierungsverantwortlichen wenigstens über emphatische Fähigkeiten verfügen würden, wären sie in der Lage, sich in die Emotionen der russischen Seele einzufühlen. Und die Sauerländer sind wohl eher nicht für ihre warme Herzlichkeit bekannt, sondern eher für ihre Sturheit.
Vorbei die Zeiten, in denen es um den Wandel durch Annäherung ging, und man den Eindruck hatte, von Politikern mit Charakter- und Herzensbildung geleitet zu werden. Das waren auch alles keine Heiligen, aber man hatte zumindest den Eindruck, sie bemühten sich um die Mehrung des Wohles für Deutschland.
Mit den richtigen Leuten an der richtigen Stelle böte die derzeitige Veränderung der Kräfteverhältnisse die einmalige Chance, dass Deutschland endlich seiner schon lange fälligen Aufgabe nachkäme, nämlich dem geistig gemeinten Spruch „Am deutschen Wesen soll die Welt genesen“ in die lebendige Tat umzusetzen. Es heißt nicht: An deutschen Waffen oder an deutscher Kriegstüchtigkeit soll Europa, soll die Welt genesen, sondern am deutschen WESEN!!!
Was macht dieses Wesen, wie es geistig gemeint ist, aus?
Deutschland blickt auf eine lange Geschichte von Denkern und Dichtern zurück. Was hat das deutsche Wesen für Komponisten hervorgebracht, welche geistige Blütezeit erlebte Deutschland in der Romantik? In der deutschen Kultur wird gut und gerne gedacht, man hat Freude am Nachdenken, am Austüfteln, am Erfinden. Das eigentliche Kapital der deutschen Kultur ist das Denkvermögen und der Verstand, sofern er sich frei entfalten kann, erst lange danach kommt die Bewertung des wirtschaftlichen Erfolges, der nur die Folge davon ist. Effiziente, hochmoderne Waffen herzustellen, ist eine Verirrung dieses Denkvermögens.
Die geografischen Verhältnisse lassen sich mit keinem Krieg verändern. Die USA bleiben da, wo sie sind, Russland im Osten auch, Frankreich im Westen ebenso.
Die USA haben eine vollkommen andere Grenzsituation, als z. B. Russland. Die USA grenzen im Norden an Kanada, im Süden an Mexico, im Osten und im Westen sind sie durch den Ozean abgegrenzt. Russland ist das flächengrößte Land der Erde mit einer Festland- Grenzlänge von rund 22.000 Kilometern. Das schafft ein komplett anderes, legitimes Schutzbedürfnis.
Deutschland liegt sowohl geographisch, als auch wirtschaftlich (noch, mehr oder weniger) im Zentrum Europas. Diese Lage mit den USA im Westen und Russland im Osten drängt Deutschland schon rein geographisch in die Situation, eigentlich der Vermittler zwischen dem Westen und dem Osten zu sein, statt sich auf eine Seite von beiden zu stellen. Dazu würde ein einvernehmliches, einträgliches Auskommen mit beiden Seiten gehören.
Um diese Aufgabe wahrzunehmen, wäre es die klügste, derzeit für die agierenden „Geistesgrößen“ aber leider unmöglich zu denkende Entscheidung, die Gelegenheit zu ergreifen, statt kriegstüchtig werden zu wollen, endlich wirklich friedensfähig zu werden, in dem, wie gesagt, für die derzeitigen „Kapazitäten“ absurd klingend, Deutschland sofort mit massiven Neutralitätsbestrebungen beginnen müsste, also vor allem zunächst einmal raus aus der NATO. Sofortiges Einstellen von Waffenlieferungen und deren Komponenten ins Ausland.
Mit der Schweiz und Österreich gibt es bereits den Ansatz der Neutralität im deutschsprachigen Kulturraum, dem Deutschland, wenn es sich anschlösse, einen gewaltigen Auftrieb geben würde. Das wäre zu Ende gedacht, die Umsetzung der derzeit hohlen Phrase: Von deutschem Boden soll nur noch Frieden ausgehen. Frieden durch Krieg herstellen zu wollen, ist paradox. Und Frieden durch Neutralität ist auch viel billiger, als Aufrüstung zur Kriegsverhinderung. Man stelle sich vor, welche Entlastung die Entscheidung für Neutralität in den Anrainerstaaten, in ganz Europa und der Welt auslösen würde. Es würde eine immense Entspannung eintreten. Im Idealfall sogar Nachahmer finden. Was wäre das für ein Signal! Was menschlich und wirtschaftlich ins Stocken geraten ist, könnte wieder ins Fließen kommen. Stattdessen soll verhindert werden, dass die Nordstream Pipeline wieder in Betrieb genommen wird. Das ist pathologischer Wirtschafts-Suizid.
Die Skeptiker mögen Gründe vorlegen, warum Russland oder sonst wer auf die Idee kommen sollte, ein neutrales Land angreifen zu wollen.
Druck erzeugt Gegendruck! Diesen Druck aufzubauen, liegt vor allem in der immer noch primitiven Veranlagung des Menschen, besonders ausgeprägt bei Männern. Wer hat den „Längeren“, und wer ihn nicht hat, der gibt stattdessen mit dem dicksten Auto an. Im übertragenen Sinne passiert das genauso in der Politik. Und Krieg ist Politik mit anderen Mitteln. Phallisch anmutende Raketen sind der äußere Ausdruck von vor allem testosterongesteuertem, spätpubertärem Imponiergehabe, und das ist dringend zu überwinden! Die Entwicklung der Menschheit könnte so einen großen Schritt nach vorne machen.
Man stelle sich vor, welche beruhigende, friedfertige Ausstrahlung vom deutschsprachigen Kulturraum ausgehen würde, wenn diese Neutralität gelebt würde.
Derzeit ist es aber eher so, dass z. B. von Scott Ritter, der lange in Deutschland war und das deutsche Wesen kennt, die Aussage kommt, dass er Deutschland in seinem Streben nach Frieden nie wirklich getraut hat, und jetzt hätte sich bestätigt, dass er richtig gelegen hat. Die Stationierung einer Brigade in Litauen ist pure Provokation und vollkommen Gaga.
Deutschland ist schon sehr weit auf dem Holzweg vorangeschritten und reitet sich immer tiefer in den Sumpf. Das Dilemma ist, dass weder in den Alt-Parteien, noch in der Opposition ein Bewusstsein dafür vorhanden ist, was wirklich zu tun wäre.
Deutschland braucht keine erstarkte Bundeswehr (weil testosterongesteuert), sondern eine Truppe von Menschen, die sich friedensbildenden Maßnahmen verschrieben hat und diese zum Wohle Deutschlands und den irren Zuständen in der ganzen Welt unter allen Umständen umsetzen will.
Auf die Deutschen, die sagen, „Ich allein kann ja sowieso nichts ändern“, kann man nicht zählen, weil sie sich ihrer Macht gar nicht bewusst sind, wenn sie in der Lage wären zu erfassen, wie viele genau dasselbe sagen.
Der Impuls muss von denjenigen ausgehen, die sich nicht mehr beweisen müssen, was für tolle Hechte sie sind, die nicht mit ihren dicken, doofen Karren und mit ihrem Haus, ihrem Pool und sonst noch was den Frauen beweisen müssen, wie potent sie noch sind.
Und auch von den Frauen, die nicht wollen, dass sie sich Sorgen um ihre Männer, Söhne, Brüder machen wollen, ob sie im besten Fall aus dem Krieg mit amputierten Gliedmaßen, traumatisiert oder gar nicht mehr nach Hause kommen. Inklusive der Omas gegen rechts vor links, die einmal bei einem Stück Sahnetorte und einem koffeinfreien Kaffee, verlängert mit heißem Wasser (mein Herz!), darüber nachdenken sollten, ob sie ihre geliebten Enkel wirklich für eine menschenfeindliche, kriegerische Ideologie verheizen lassen wollen.
Das ist ein Appell an die vielen verirrten Seelen an den Schalthebeln: Denkt bitte einmal darüber nach, ob es wirklich sinnvoll ist, mit rheinmetallischen Waffen abschrecken zu wollen, oder ob es nicht vielleicht menschenwesensgerechter wäre, durch wirklich umsetzbare, an der Lebensrealität gemessenen friedensbildenden Maßnahmen den Dampf aus dem Kessel zu nehmen. Würdet ihr nämlich darüber ernsthaft nachdenken, würde euch ganz schnell klar werden, dass eure Strategie, eure sogenannten Friedensvorschläge, eure Vorstellungen nicht mit der Realität vereinbar sind.
Dieser Artikel wurde mit dem Pareto-Client geschrieben
* *
(Bild von pixabay)
-
 @ 7f6db517:a4931eda
2025-05-27 04:01:32
@ 7f6db517:a4931eda
2025-05-27 04:01:32
The former seems to have found solid product market fit. Expect significant volume, adoption, and usage going forward.
The latter's future remains to be seen. Dependence on Tor, which has had massive reliability issues, and lack of strong privacy guarantees put it at risk.
— ODELL (@ODELL) October 27, 2022
The Basics
- Lightning is a protocol that enables cheap and fast native bitcoin transactions.
- At the core of the protocol is the ability for bitcoin users to create a payment channel with another user.
- These payment channels enable users to make many bitcoin transactions between each other with only two on-chain bitcoin transactions: the channel open transaction and the channel close transaction.
- Essentially lightning is a protocol for interoperable batched bitcoin transactions.
- It is expected that on chain bitcoin transaction fees will increase with adoption and the ability to easily batch transactions will save users significant money.
- As these lightning transactions are processed, liquidity flows from one side of a channel to the other side, on chain transactions are signed by both parties but not broadcasted to update this balance.
- Lightning is designed to be trust minimized, either party in a payment channel can close the channel at any time and their bitcoin will be settled on chain without trusting the other party.
There is no 'Lightning Network'
- Many people refer to the aggregate of all lightning channels as 'The Lightning Network' but this is a false premise.
- There are many lightning channels between many different users and funds can flow across interconnected channels as long as there is a route through peers.
- If a lightning transaction requires multiple hops it will flow through multiple interconnected channels, adjusting the balance of all channels along the route, and paying lightning transaction fees that are set by each node on the route.
Example: You have a channel with Bob. Bob has a channel with Charlie. You can pay Charlie through your channel with Bob and Bob's channel with User C.
- As a result, it is not guaranteed that every lightning user can pay every other lightning user, they must have a route of interconnected channels between sender and receiver.
Lightning in Practice
- Lightning has already found product market fit and usage as an interconnected payment protocol between large professional custodians.
- They are able to easily manage channels and liquidity between each other without trust using this interoperable protocol.
- Lightning payments between large custodians are fast and easy. End users do not have to run their own node or manage their channels and liquidity. These payments rarely fail due to professional management of custodial nodes.
- The tradeoff is one inherent to custodians and other trusted third parties. Custodial wallets can steal funds and compromise user privacy.
Sovereign Lightning
- Trusted third parties are security holes.
- Users must run their own node and manage their own channels in order to use lightning without trusting a third party. This remains the single largest friction point for sovereign lightning usage: the mental burden of actively running a lightning node and associated liquidity management.
- Bitcoin development prioritizes node accessibility so cost to self host your own node is low but if a node is run at home or office, Tor or a VPN is recommended to mask your IP address: otherwise it is visible to the entire network and represents a privacy risk.
- This privacy risk is heightened due to the potential for certain governments to go after sovereign lightning users and compel them to shutdown their nodes. If their IP Address is exposed they are easier to target.
- Fortunately the tools to run and manage nodes continue to get easier but it is important to understand that this will always be a friction point when compared to custodial services.
The Potential Fracture of Lightning
- Any lightning user can choose which users are allowed to open channels with them.
- One potential is that professional custodians only peer with other professional custodians.
- We already see nodes like those run by CashApp only have channels open with other regulated counterparties. This could be due to performance goals, liability reduction, or regulatory pressure.
- Fortunately some of their peers are connected to non-regulated parties so payments to and from sovereign lightning users are still successfully processed by CashApp but this may not always be the case going forward.
Summary
- Many people refer to the aggregate of all lightning channels as 'The Lightning Network' but this is a false premise. There is no singular 'Lightning Network' but rather many payment channels between distinct peers, some connected with each other and some not.
- Lightning as an interoperable payment protocol between professional custodians seems to have found solid product market fit. Expect significant volume, adoption, and usage going forward.
- Lightning as a robust sovereign payment protocol has yet to be battle tested. Heavy reliance on Tor, which has had massive reliability issues, the friction of active liquidity management, significant on chain fee burden for small amounts, interactivity constraints on mobile, and lack of strong privacy guarantees put it at risk.
If you have never used lightning before, use this guide to get started on your phone.
If you found this post helpful support my work with bitcoin.

-
 @ 7f6db517:a4931eda
2025-05-27 04:01:32
@ 7f6db517:a4931eda
2025-05-27 04:01:32
Bank run on every crypto bank then bank run on every "real" bank.
— ODELL (@ODELL) December 14, 2022
The four main banks of bitcoin and “crypto” are Signature, Prime Trust, Silvergate, and Silicon Valley Bank. Prime Trust does not custody funds themselves but rather maintains deposit accounts at BMO Harris Bank, Cross River, Lexicon Bank, MVB Bank, and Signature Bank. Silvergate and Silicon Valley Bank have already stopped withdrawals. More banks will go down before the chaos stops. None of them have sufficient reserves to meet withdrawals.
Bitcoin gives us all the ability to opt out of a system that has massive layers of counterparty risk built in, years of cheap money and broken incentives have layered risk on top of risk throughout the entire global economy. If you thought the FTX bank run was painful to watch, I have bad news for you: every major bank in the world is fractional reserve. Bitcoin held in self custody is unique in its lack of counterparty risk, as global market chaos unwinds this will become much more obvious.
The rules of bitcoin are extremely hard to change by design. Anyone can access the network directly without a trusted third party by using their own node. Owning more bitcoin does not give you more control over the network with all participants on equal footing.
Bitcoin is:
- money that is not controlled by a company or government
- money that can be spent or saved without permission
- money that is provably scarce and should increase in purchasing power with adoptionBitcoin is money without trust. Whether you are a nation state, corporation, or an individual, you can use bitcoin to spend or save without permission. Social media will accelerate the already deteriorating trust in our institutions and as this trust continues to crumble the value of trust minimized money will become obvious. As adoption increases so should the purchasing power of bitcoin.
A quick note on "stablecoins," such as USDC - it is important to remember that they rely on trusted custodians. They have the same risk as funds held directly in bank accounts with additional counterparty risk on top. The trusted custodians can be pressured by gov, exit scam, or caught up in fraud. Funds can and will be frozen at will. This is a distinctly different trust model than bitcoin, which is a native bearer token that does not rely on any centralized entity or custodian.
Most bitcoin exchanges have exposure to these failing banks. Expect more chaos and confusion as this all unwinds. Withdraw any bitcoin to your own wallet ASAP.
Simple Self Custody Guide: https://werunbtc.com/muun
More Secure Cold Storage Guide: https://werunbtc.com/coldcard
If you found this post helpful support my work with bitcoin.

-
 @ eb0157af:77ab6c55
2025-05-26 12:01:37
@ eb0157af:77ab6c55
2025-05-26 12:01:37A new study reveals: 4 out of 5 Americans would like the US to convert some of its gold into Bitcoin.
A recent survey conducted by the Nakamoto Project revealed that a majority of Americans support converting a portion of the United States’ gold reserves into Bitcoin. The survey, carried out online by Qualtrics between February and March 2025, involved 3,345 participants with demographic characteristics representative of US census standards. Most respondents expressed a desire to convert between 1% and 30% of the gold reserves into BTC.
Troy Cross, co-founder of the Nakamoto Project, stated:
“When given a slider and asked to advise the US government on the right proportion of Bitcoin and gold, subjects were very reluctant to put that slider on 0% Bitcoin and 100% gold. Instead, they settled around 10% Bitcoin.”
One significant finding from the research is the correlation between age and openness to Bitcoin: younger respondents showed a greater inclination toward the cryptocurrency compared to older generations.
A potential US strategy
Bo Hines, a White House advisor, is promoting an initiative for the Treasury Department to acquire Bitcoin by selling off a portion of its gold. Under the proposed plan, the government could acquire up to 1 million BTC over the next five years.
To finance these purchases, the government plans to sell Federal Reserve gold certificates. The proposal aligns with Senator Cynthia Lummis’ 2025 Bitcoin Act, which aims to declare Bitcoin a critical national strategic asset.
Currently, the United States holds 8,133 metric tons of gold, valued at over $830 billion, and about 200,000 BTC, valued at $21 billion.
The post The majority in the US wants to convert part of the gold reserves into Bitcoin appeared first on Atlas21.
-
 @ 58537364:705b4b85
2025-05-26 11:43:15
@ 58537364:705b4b85
2025-05-26 11:43:15สมัยนี้คนบูชาเสรีภาพโดยตามใจกิเลส ยุคที่...กลายเป็นปีศาจในร่างของมนุษย์

ในมหาวิทยาลัยนี่ ก็ลองคิดดูซิ ก็มีการทะเลาะวิวาทกัน อย่างอันธพาลในหมู่นักศึกษานิสิตกันเอง, ไม่เคารพครูบาอาจารย์ เห็นครูบาอาจารย์เป็นลูกจ้าง, แล้วก็ไม่มีใครว่าอะไรใคร ไม่มีใครเห็นว่ามันเป็นของผิด ถ้าเป็นอย่างนั้นสมัยก่อน เพียง ๕๐ - ๖๐ ปีมาแล้ว เขาประณามเป็นเรื่องเสียหาย เป็นเรื่องที่จะไม่มีอะไรที่น่าอับอายขายหน้าเท่ากับสิ่งเหล่านั้น
ถ้าในสํานักศึกษาอันเป็นที่สร้างดวงจิตดวงวิญญาณของมนุษย์เป็นอย่างนี้เสียแล้ว แล้วนอกนั้นมันจะเป็นอย่างไร? เพราะอะไรๆก็ออกไปจากสํานักศึกษา, เพราะว่าเราต้องผ่านสํานักการศึกษา จนกว่าจะเติบโตแล้วออกไป ถ้าในสํานักสําหรับการศึกษานั้น เป็นแหล่งเพาะวิญญาณของซาตาน ของวัตถุนิยมเสียแล้ว มันก็หมดกัน ไม่มีอะไรเหลือ
ฉะนั้น ถ้าใครยังรักบ้านรักเมือง รักเกียรติยศของความเป็นมนุษย์แล้ว, ก็ช่วยกันไปคิดให้ดีๆ ช่วยกันต่อต้านไว้บ้าง อย่าไปตามกันอาจารย์ฝรั่งไปเสียทุกอย่างทุกทาง...ฯ
สมัยนี้คนบูชาเสรีภาพโดยตามใจกิเลส. ยังมีสิ่งที่ร้ายกาจอีกสิ่งหนึ่ง ก็คือสิ่งที่เรียกว่า “เสรีภาพ” ทุกคนบูชาเสรีภาพ แต่มันเป็นเสรีภาพเพื่อจะเป็นภูตผีปีศาจ หรือเป็นสัตว์เดรัจฉานในที่สุด. เสรีภาพของเขาต้องการอย่างนี้ : ต้องการจะเสรีภาพตามใจกิเลส ตามใจซาตาน ตามใจพญามาร ไม่มีศีลธรรม. นี่เขาต้องการเสรีภาพอย่างนี้ : อยากจะไว้ผมยาว, อยากจะแต่งตัวให้แปลกประหลาด, อยากจะมีเสรีภาพ ไม่รู้ว่า เสรีภาพอะไรกัน
ทีนี้ เสรีภาพที่เป็นอันตรายที่สุด ก็คือการแสดงอะไรได้ตามชอบใจ : เขียนก็จะเขียนได้ตามชอบใจ, จะแสดงศิลปอะไรก็แสดงได้ตามชอบใจ, ไม่ถือว่าเป็นลามกอนาจาร สิ่งที่เป็นลามกอนาจาร ก็บัญญัติกันเสียใหม่ว่า ไม่ใช่ลามกอนาจาร
เรื่องที่เขาแก้ไขกันเสียใหม่ว่าไม่ลามกอนาจารนะ มันมากมายด้วยกัน : การประกวดนางหน้าด้านนั้น, ก็กลายเป็นของดีของวิเศษ ของอะไรไป ทั่วโลกสมัยนี้เขาเห็นเป็นสิ่งที่ถูกต้องที่ดีที่สุด ประกวดกันทุกหนทุกแห่งในโลกนี้ ผมเรียกว่าประกวดนางหน้าด้าน ถ้าหน้าไม่ด้านพอ ก็ไปเปิดแข้งเปิดขาเปิดอะไร แสดงอย่างนั้นไม่ได้
ถ้าเป็นสมัยก่อน คุณย่า คุณยาย เป็นลมตายแน่ ถ้าลูกหลานของแกไปทําอย่างนั้น เดี๋ยวนี้ เขาเห็นว่าถูกต้องดีงามไปหมด; นี่ก็คือ “เสรีภาพ” ผลของเสรีภาพมันเป็นอย่างนี้ นี้เป็นเรื่องที่เห็นได้ชัดๆ โต้งๆ แล้วที่มันยังละเอียด เห็นได้ยาก แฝงอยู่ในอะไรต่างๆ ยังมีอีกมาก
เสรีภาพในการเขียน ไม่มีใครว่าใครได้ แล้วก็เขียนเรื่องลามก อนาจาร ลงไปในหนังสือประจําวัน, แพร่หลายทั่วไปหมด ; ย้อมนิสัยเด็กๆ ให้เสียไปโดยไม่รู้สึกตัว, โดยไม่ต้องรู้สึกตัว, เขียนเรื่องอ่านเล่นโดยนามปากกา ที่มีชื่อเสียง นิยมนับถือกันทั้งประเทศ แต่แล้วก็เขียนเรื่องที่ทําให้เด็กมีจิตใจเลวทราม, เสื่อมเสียทางศีลธรรมโดยไม่รู้สึกตัว คุณไปเอาหนังสือพิมพ์มาพิจารณาดูเอาก็แล้วกัน ก็จะมองเห็น
ยังมีอะไรอีกมาก ที่ทําให้เด็กๆกลายเป็นปีศาจในร่างมนุษย์, มีอีกมาก ทําให้คนเรากลายเป็นปีศาจในร่างมนุษย์, คนโต ๆ ไม่เป็นไร, ไม่กี่ปีก็ตาย แต่ว่าการที่ทําให้เด็กๆ มากลายเป็นอย่างนั้นนั้น มันน่าอันตรายอย่างยิ่ง เพราะว่าเขายังจะอยู่ไปอีกนาน
การพูดจาก็ดี การเขียนก็ดี ศิลปวัตถุ นิทรรศการ ภาพยนตร์ อะไรต่าง ๆ ล้วนแต่เป็นอย่างเดียวกันหมด เขามีเสรีภาพ มีอิสรภาพ มีเสรีภาพที่จะทํา, ใครห้ามกันไม่ได้ หรือบางทีเขาก็มีอํานาจอย่างอื่น มาช่วยให้เขาต้องทําหรือได้ทํา
เมื่ออ้างเสรีภาพไม่ได้ ก็ใช้อํานาจอย่างอื่นมาช่วยให้ได้ทํา เขาก็ทํากันทั่วไปหมดทุกหนทุกแห่ง ทุกหัวระแหง, ทําลูกเด็ก ๆ ของเราให้กลายเป็นปีศาจในร่างมนุษย์นมากขึ้นๆเหลือที่จะป้องกัน, เหลือที่จะแก้ไขแล้ว นี่แหละ คือรากฐานอันแท้จริงของการเสื่อมทางศีลธรรม, แล้วเรื่องอื่นๆ มันก็ต้องตามมาแน่นอน ; เรื่องอันธพาล, เรื่องอะไรก็ตาม มันก็ต้องตามมามากเหลือที่จะประมาณได้
นี้มันก็ไม่ใช่เรื่องเล็กน้อย เป็นเรื่องทั้งหมดของมนุษย์ หรือของโลกมนุษย์ ที่จะอยู่หรือว่าจะล่มจม มีมูลมาจากการศึกษาแผนใหม่ วัฒนธรรมแผนใหม่ ที่มาจากข้างนอก เข้ามาสู่ประเทศไทย, เรียกว่าเราอยู่ในยุคของอะไร ลองคิดดู พวกเรากําลังอยู่ในยุคอะไร? ควรจะเรียกชื่อของยุคนี้ว่ายุคอะไร ลองคิดดู ? ส่วนผมนั้น สมัครเรียกว่า ยุคที่กลายเป็นปีศาจในร่างของมนุษย์..
พุทธทาสภิกขุ ที่มา : ธรรมเทศนาชุดชุมนุมล้ออายุ หัวข้อเรื่อง “ยิ่งจะทำให้ดี, โลกมันยิ่งบ้า” เมื่อวันที่ ๒๗ พฤษภาคม ๒๕๑๓ กัณฑ์ค่ำ ณ ลานหินโค้ง จากหนังสือชุดธรรมโฆษณ์ เล่มชื่อว่า “ชุมนุมล้ออายุ เล่ม ๑” หน้า ๕๑๕-๕๑๖,๕๑๙-๕๒๑
-
 @ 9ca447d2:fbf5a36d
2025-05-26 11:01:16
@ 9ca447d2:fbf5a36d
2025-05-26 11:01:16KYC database of Coinbase, the largest U.S. digital asset exchange, has been breached and up to 1% of monthly active users, or around 100,000 customers, have had their personal info stolen.
Hackers reportedly bribed overseas customer support agents and contractors to leak internal company info and user data. They then demanded $20 million and threatened to release the stolen data if Coinbase didn’t pay.
Instead of paying the ransom, Coinbase said no and is setting up a $20 million reward fund for anyone who can help catch the hackers.
“They then tried to extort Coinbase for $20 million to cover this up. We said no,” the company said in a blog post. “Instead of paying the $20 million ransom, we’re establishing a $20 million reward fund.”
So what’s been stolen? The breach, which was first disclosed in a filing with the U.S. Securities and Exchange Commission (SEC), did not involve any theft of customer funds, login credentials, private keys or wallets.
But the hackers did get:
- Full names
- Addresses
- Phone numbers
- Email addresses
- Last 4 digits of Social Security numbers
- Bank account numbers and some bank identifiers
- Government ID images (driver’s licenses, passports, etc.)
- Account balances and transaction history
- Internal corporate documents and training materials
Coinbase says Prime accounts were not affected and no passwords or 2FA codes were stolen.
According to Coinbase, the attackers targeted outsourced support agents in countries like India. They were offering cash bribes in exchange for access to the company’s internal customer support tools.
“What these attackers were doing was finding Coinbase employees and contractors based in India who were associated with our business process outsourcing or support operations, that kind of thing, and bribing them in order to obtain customer data,” said Philip Martin, Coinbase’s Chief Security Officer.
Coinbase said it first saw suspicious activity in January 2025 but didn’t get a direct email from the threat actors until May 11. The email had evidence of stolen data and the ransom demand.
Coinbase quickly launched an investigation, fired all the involved support agents and notified law enforcement. It also started notifying users via email on May 15.
The Coinbase data breach has hit it hard, financially and publicly. The company estimates it will spend $180-$400 million on security upgrades, reimbursements and other remediation.
Coinbase’s stock also took a hit, dropping 6.4% after the news broke, before rebounding.
Analysts say this couldn’t have come at a worse time, as Coinbase is about to be added to the S&P 500 index – a big deal for any publicly traded company.
It’s definitely an unfortunate timing. “This may push the industry to adopt stricter employee vetting and introduce some reputational risks,” said Bo Pei, analyst at U.S. Tiger Securities.
Coinbase will reimburse any customers who were tricked into sending their digital assets to the attackers as part of social engineering scams. They’ve also introduced new security measures:
- Extra ID verification for high-risk withdrawals
- Scam-awareness prompts
- A new U.S.-based support center
- Stronger insider threat monitoring
- Simulation testing for internal systems
Affected customers have already been notified and the exchange is working with U.S. and international law enforcement to track down the attackers.
This is part of a larger trend in the digital assets world. Earlier this year, Bybit, another exchange, was hit with a $1.5 billion theft, dubbed the biggest digital asset heist in history.
Research from Chainalysis shows over $2.2 billion was stolen from digital asset platforms in 2024 alone.
-
 @ 7f6db517:a4931eda
2025-05-27 04:01:31
@ 7f6db517:a4931eda
2025-05-27 04:01:31
The newly proposed RESTRICT ACT - is being advertised as a TikTok Ban, but is much broader than that, carries a $1M Fine and up to 20 years in prison️! It is unconstitutional and would create massive legal restrictions on the open source movement and free speech throughout the internet.
The Bill was proposed by: Senator Warner, Senator Thune, Senator Baldwin, Senator Fischer, Senator Manchin, Senator Moran, Senator Bennet, Senator Sullivan, Senator Gillibrand, Senator Collins, Senator Heinrich, and Senator Romney. It has broad support across Senators of both parties.
Corrupt politicians will not protect us. They are part of the problem. We must build, support, and learn how to use censorship resistant tools in order to defend our natural rights.
The RESTRICT Act, introduced by Senators Warner and Thune, aims to block or disrupt transactions and financial holdings involving foreign adversaries that pose risks to national security. Although the primary targets of this legislation are companies like Tik-Tok, the language of the bill could potentially be used to block or disrupt cryptocurrency transactions and, in extreme cases, block Americans’ access to open source tools or protocols like Bitcoin.
The Act creates a redundant regime paralleling OFAC without clear justification, it significantly limits the ability for injured parties to challenge actions raising due process concerns, and unlike OFAC it lacks any carve-out for protected speech. COINCENTER ON THE RESTRICT ACT
If you found this post helpful support my work with bitcoin.

-
 @ eb0157af:77ab6c55
2025-05-26 09:01:22
@ eb0157af:77ab6c55
2025-05-26 09:01:22According to the ECB Executive Board member, the launch of the digital euro depends on the timing of the EU regulation.
The European Central Bank (ECB) is making progress in preparing for the digital euro. According to Piero Cipollone, ECB Executive Board member and coordinator of the project, the technical phase “is proceeding quickly and on schedule,” but moving to operational implementation still requires political approval of the regulation at the European level.
Speaking at the ‘Voices on the Future’ event organized by Ansa and Asvis, Cipollone outlined a possible timeline:
“If the regulation is approved at the start of 2026 — in the best-case scenario for the European legislative process — we could see the first transactions with the digital euro by mid-2028.”
Cipollone also highlighted Europe’s current dependence on electronic payment systems managed by non-European companies:
“Today in Europe, whenever we don’t use cash, any transaction online or at the supermarket has to go through credit cards, with their fees. The payment system relies on companies that aren’t based in Europe. You can see why it would make sense to have a system fully under our control.”
For the ECB board member, the digital euro would act as a direct alternative to cash in the digital world, working like “a banknote you can spend anywhere in Europe for any purpose.”
The digital euro project is part of the ECB’s broader strategy to strengthen the independence of Europe’s financial system. According to Cipollone and the Central Bank, Europe’s digital currency would be a key step toward greater autonomy in electronic payments, reducing reliance on infrastructure and services outside the European Union.
The post ECB: digital euro by mid-2028, says Cipollone appeared first on Atlas21.
-
 @ 7f6db517:a4931eda
2025-05-27 04:01:31
@ 7f6db517:a4931eda
2025-05-27 04:01:31
@matt_odell don't you even dare not ask about nostr!
— Kukks (Andrew Camilleri) (@MrKukks) May 18, 2021
Nostr first hit my radar spring 2021: created by fellow bitcoiner and friend, fiatjaf, and released to the world as free open source software. I was fortunate to be able to host a conversation with him on Citadel Dispatch in those early days, capturing that moment in history forever. Since then, the protocol has seen explosive viral organic growth as individuals around the world have contributed their time and energy to build out the protocol and the surrounding ecosystem due to the clear need for better communication tools.
nostr is to twitter as bitcoin is to paypal
As an intro to nostr, let us start with a metaphor:
twitter is paypal - a centralized platform plagued by censorship but has the benefit of established network effects
nostr is bitcoin - an open protocol that is censorship resistant and robust but requires an organic adoption phase
Nostr is an open communication protocol that can be used to send messages across a distributed set of relays in a censorship resistant and robust way.
- Anyone can run a relay.
- Anyone can interact with the protocol.
- Relays can choose which messages they want to relay.
- Users are identified by a simple public private key pair that they can generate themselves.Nostr is often compared to twitter since there are nostr clients that emulate twitter functionality and user interface but that is merely one application of the protocol. Nostr is so much more than a mere twitter competitor. Nostr clients and relays can transmit a wide variety of data and clients can choose how to display that information to users. The result is a revolution in communication with implications that are difficult for any of us to truly comprehend.
Similar to bitcoin, nostr is an open and permissionless protocol. No person, company, or government controls it. Anyone can iterate and build on top of nostr without permission. Together, bitcoin and nostr are incredibly complementary freedom tech tools: censorship resistant, permissionless, robust, and interoperable - money and speech protected by code and incentives, not laws.
As censorship throughout the world continues to escalate, freedom tech provides hope for individuals around the world who refuse to accept the status quo. This movement will succeed on the shoulders of those who choose to stand up and contribute. We will build our own path. A brighter path.
My Nostr Public Key: npub1qny3tkh0acurzla8x3zy4nhrjz5zd8l9sy9jys09umwng00manysew95gx
If you found this post helpful support my work with bitcoin.

-
 @ 21335073:a244b1ad
2025-03-18 14:43:08
@ 21335073:a244b1ad
2025-03-18 14:43:08Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ 69eea734:4ae31ae6
2025-05-26 01:15:05
@ 69eea734:4ae31ae6
2025-05-26 01:15:05Dies ist der Anfang einer Serie, die ich schreiben möchte. Sie handelt von etwas, das wir verloren haben, und das dennoch, in Teilen, in uns weiterlebt.
Wen meine ich mit dem “wir”? Das Wir kann schnell problematisch werden, wenn man meint für andere zu sprechen, und dann erkennen muss, falsche Annahmen gemacht zu haben.
Als ich diesen Satz schrieb, hatte ich diejenigen von uns im Hinterkopf, die in einer westlichen Industriegesellschaft aufgewachsen sind. Der Verlust ist etwas, das ich spüre, und dem reale Geschehnisse mit zugrunde liegen. Eine Art Sehnsucht wird stärker, wenn ich von bestimmten Ereignissen lese, bei denen Menschen gewaltsam von dem getrennt wurden, das sie bis dahin gehalten und ernährt hatte: Dem Land, zu dem sie gehörten.
Worüber ich schreiben möchte, das sind die Commons. Ein weites Feld. Commons, das kann Allmende heißen oder Gemeingüter.
Es geht dabei aber nicht nur um das, was gemeinsam genutzt wird, sondern auch um das Soziale darum herum — wie sich eine Gruppe selbst organisiert, und dabei den Mitgliedern und dem Gemeingut gerecht wird
Es ist eines jener Konzepte, denen mit einer einfachen Definition nicht gut gedient ist. Es geht eher darum, ein Gefühl dafür zu bekommen, sich ihm anzunähern, eine Beziehung aufzubauen. Wenn das gelingt, dann ist man an einer Art neuem Ort, einer neuen (und gleichzeitig alten) Sichtweise angekommen, die man nicht mehr verliert. Und gleichzeitig Teil einer Gemeinschaft geworden.
Zum Commons gehören Personen und das Commoning. Subjekte und ein Verb. Hinzu kommen die Resourcen, die gemeinsam betreut werden. Also Subjekt, Verb, Objekt. Hilfreicher ist es, die Ressourcen ebenfalls als Subjekte zu sehen. Beim ursprünglichen Commons stand der Commoner in einer partnerschaftlichen Beziehung zu dem Land, das seine Lebensgrundlage war. [1]
Die Commons bilden ein Gegengewicht zu Staat und Privatwirtschaft. Sie funktionieren nach einer anderen Logik, und wirken der kapitalistischen Forderung nach exponentiellem Wachstum, und der Vereinzelung der Menschen in der modernen Gesellschaft entgegen.
Mein Vorhaben ist, alle ein bis zwei Wochen einen kurzen Aufsatz zu schreiben, der einen Aspekt der Commons beleuchtet. Der deutsche Wikipedia-Eintrag gibt sehr gut wieder, wie vielschichtig das Thema ist.
Es könnte dabei in folgende Richtungen gehen:
- Geschichte der Enclosures (Einhegungen)
- Kämpfe indigener Kulturen und anarchischer Gemeinschaften
- Bemühungen, Commons und das Commoning in unserer westlichen Kulturn wiederzubeleben und zu fördern
- Das kollektive Trauma, das mit dem Verlust von Gemeingütern, insbesondere Land, verbunden ist
- Wie sich dies in jedem Einzelnen widerspiegelt
Ich schreibe dabei auch, um mir selbst über bestimmte Dinge klar zu werden. Ich bin mit zwei Commons-Bewegungen im Südwesten Englands verbunden, und diese Beziehungen sind nicht immer ganz einfach. Und doch würde ich mich nicht davon lösen wollen.
Warum schrieb ich davon, dass wir etwas verloren haben, wenn es die Commons doch gibt?
Eine bestimmte Lebensweise, die freien Zugang zu Wald und Acker- und Weideland garantierte, um sich zu ernähren und Holz und Torf zu sammeln, wurde mit den Einhegungen nach und nach zerstört. Während das Leben sicher sehr hart war — und sich zuvor innerhalb der Feudalherrschaft abspielte — sorgten über lange Zeit gewachsene Traditionen und Bräuche dafür, dass Menschen sich zugehörig und versorgt fühlten. Diese Art des Aufgehobenseins ging verloren, als die Landbewohner vertrieben wurden und sich in den Städten als Lohnarbeiter verdingen oder auswandern mussten.
Vor kurzem habe ich ein Buch namens The Traumatised Society gelesen, in dem Fred Harrison das Schicksal des englischen Naturdichters John Clare schildert, der direkt miterlebte, wie das Land eingegrenzt wurde und darüber verzweifelte. Besonders eindrücklich schreibt auch Alastair McIntosh in dem insgesamt sehr erstaunlichen und magischen Buch Soil and Soul über die schottische Version der Einhegungen, die Highland Clearances.
Solche Schilderungen lassen ahnen, wie gewaltsam die Menschen von ihrer früheren Lebensweise getrennt wurden. Später gingen England und andere europäische Mächte in ihren Kolonien ähnlich vor. Die erste Kolonisierung war die der eigenen Bevölkerung. Ich glaube, dass diese Vorgänge uns kollektiv geprägt haben, und wir die Commons brauchen, um den Folgen entgegenzuwirken.
Diese haben aber auch in ihren neueren Formen keinen leichten Stand.
Wie Silke Helfrich schrieb: “Commons existieren nicht in einer heilen Welt, sondern in einer commons-unfreundlichen Umgebung. Es ist daher wichtig, dass Commoners sich bewusst sind, welchen Schatz sie in den Händen halten, um ihn bewahren und entfalten zu können.”
Demnächst mehr...
\ [1] Der amerikanische Priester und Gelehrte Thomas Berry rief dazu auf, das Universum nicht als eine Ansammlung von Objekten zu sehen, sondern eine Gemeinschaft von Subjekten: The universe is a communion of subjects, not a collection of objects.
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 7f6db517:a4931eda
2025-05-27 04:01:31
@ 7f6db517:a4931eda
2025-05-27 04:01:31

"Privacy is necessary for an open society in the electronic age. Privacy is not secrecy. A private matter is something one doesn't want the whole world to know, but a secret matter is something one doesn't want anybody to know. Privacy is the power to selectively reveal oneself to the world." - Eric Hughes, A Cypherpunk's Manifesto, 1993
Privacy is essential to freedom. Without privacy, individuals are unable to make choices free from surveillance and control. Lack of privacy leads to loss of autonomy. When individuals are constantly monitored it limits our ability to express ourselves and take risks. Any decisions we make can result in negative repercussions from those who surveil us. Without the freedom to make choices, individuals cannot truly be free.
Freedom is essential to acquiring and preserving wealth. When individuals are not free to make choices, restrictions and limitations prevent us from economic opportunities. If we are somehow able to acquire wealth in such an environment, lack of freedom can result in direct asset seizure by governments or other malicious entities. At scale, when freedom is compromised, it leads to widespread economic stagnation and poverty. Protecting freedom is essential to economic prosperity.
The connection between privacy, freedom, and wealth is critical. Without privacy, individuals lose the freedom to make choices free from surveillance and control. While lack of freedom prevents individuals from pursuing economic opportunities and makes wealth preservation nearly impossible. No Privacy? No Freedom. No Freedom? No Wealth.
Rights are not granted. They are taken and defended. Rights are often misunderstood as permission to do something by those holding power. However, if someone can give you something, they can inherently take it from you at will. People throughout history have necessarily fought for basic rights, including privacy and freedom. These rights were not given by those in power, but rather demanded and won through struggle. Even after these rights are won, they must be continually defended to ensure that they are not taken away. Rights are not granted - they are earned through struggle and defended through sacrifice.
If you found this post helpful support my work with bitcoin.

-
 @ 7f6db517:a4931eda
2025-05-27 04:01:31
@ 7f6db517:a4931eda
2025-05-27 04:01:31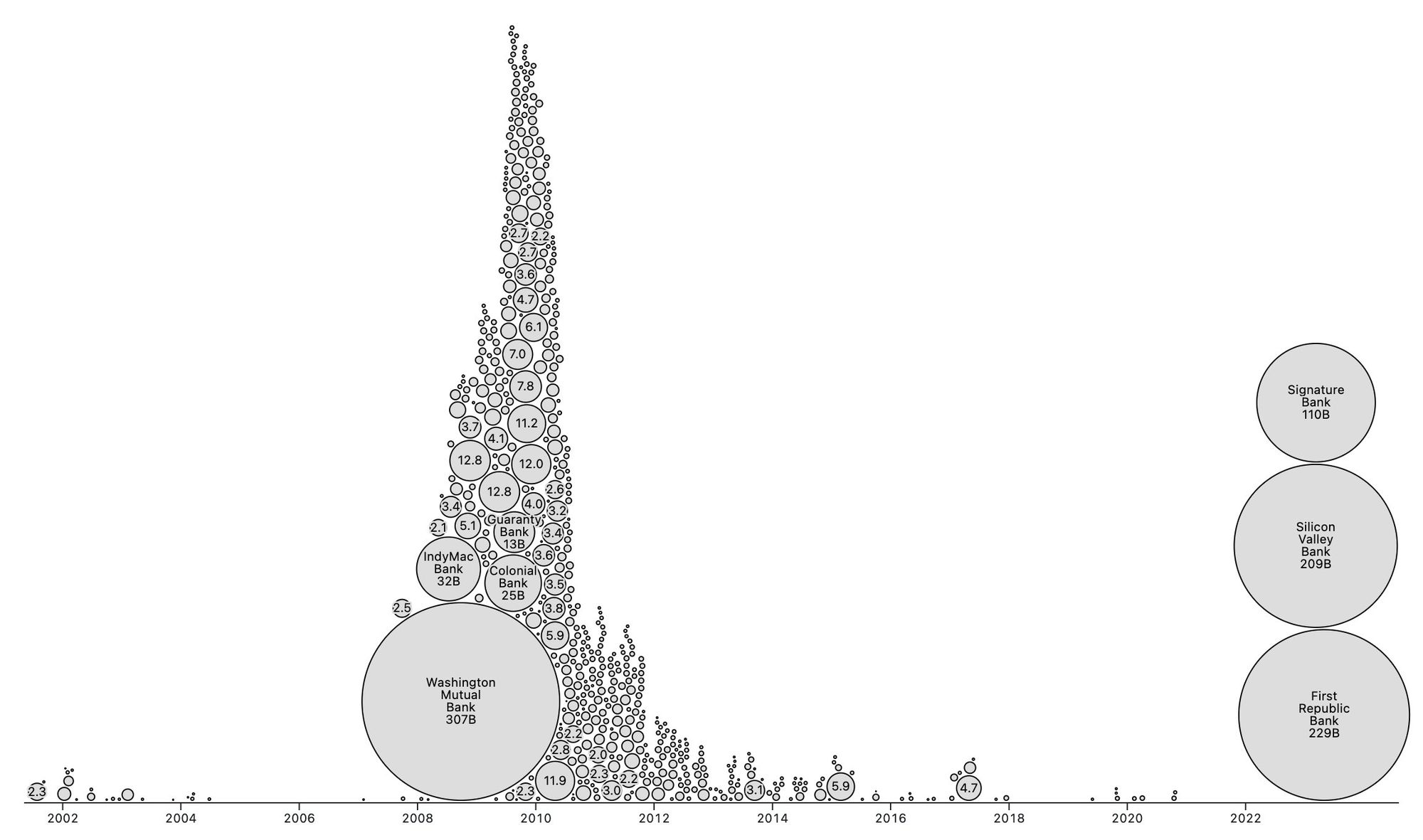
People forget Bear Stearns failed March 2008 - months of denial followed before the public realized how bad the situation was under the surface.
Similar happening now but much larger scale. They did not fix fundamental issues after 2008 - everything is more fragile.
The Fed preemptively bailed out every bank with their BTFP program and First Republic Bank still failed. The second largest bank failure in history.
There will be more failures. There will be more bailouts. Depositors will be "protected" by socializing losses across everyone.
Our President and mainstream financial pundits are currently pretending the banking crisis is over while most banks remain insolvent. There are going to be many more bank failures as this ponzi system unravels.
Unlike 2008, we have the ability to opt out of these broken and corrupt institutions by using bitcoin. Bitcoin held in self custody is unique in its lack of counterparty risk - you do not have to trust a bank or other centralized entity to hold it for you. Bitcoin is also incredibly difficult to change by design since it is not controlled by an individual, company, or government - the supply of dollars will inevitably be inflated to bailout these failing banks but bitcoin supply will remain unchanged. I do not need to convince you that bitcoin provides value - these next few years will convince millions.
If you found this post helpful support my work with bitcoin.

-
 @ 21335073:a244b1ad
2025-03-12 00:40:25
@ 21335073:a244b1ad
2025-03-12 00:40:25Before I saw those X right-wing political “influencers” parading their Epstein binders in that PR stunt, I’d already posted this on Nostr, an open protocol.
“Today, the world’s attention will likely fixate on Epstein, governmental failures in addressing horrific abuse cases, and the influential figures who perpetrate such acts—yet few will center the victims and survivors in the conversation. The survivors of Epstein went to law enforcement and very little happened. The survivors tried to speak to the corporate press and the corporate press knowingly covered for him. In situations like these social media can serve as one of the only ways for a survivor’s voice to be heard.
It’s becoming increasingly evident that the line between centralized corporate social media and the state is razor-thin, if it exists at all. Time and again, the state shields powerful abusers when it’s politically expedient to do so. In this climate, a survivor attempting to expose someone like Epstein on a corporate tech platform faces an uphill battle—there’s no assurance their voice would even break through. Their story wouldn’t truly belong to them; it’d be at the mercy of the platform, subject to deletion at a whim. Nostr, though, offers a lifeline—a censorship-resistant space where survivors can share their truths, no matter how untouchable the abuser might seem. A survivor could remain anonymous here if they took enough steps.
Nostr holds real promise for amplifying survivor voices. And if you’re here daily, tossing out memes, take heart: you’re helping build a foundation for those who desperately need to be heard.“
That post is untouchable—no CEO, company, employee, or government can delete it. Even if I wanted to, I couldn’t take it down myself. The post will outlive me on the protocol.
The cozy alliance between the state and corporate social media hit me hard during that right-wing X “influencer” PR stunt. Elon owns X. Elon’s a special government employee. X pays those influencers to post. We don’t know who else pays them to post. Those influencers are spurred on by both the government and X to manage the Epstein case narrative. It wasn’t survivors standing there, grinning for photos—it was paid influencers, gatekeepers orchestrating yet another chance to re-exploit the already exploited.
The bond between the state and corporate social media is tight. If the other Epsteins out there are ever to be unmasked, I wouldn’t bet on a survivor’s story staying safe with a corporate tech platform, the government, any social media influencer, or mainstream journalist. Right now, only a protocol can hand survivors the power to truly own their narrative.
I don’t have anything against Elon—I’ve actually been a big supporter. I’m just stating it as I see it. X isn’t censorship resistant and they have an algorithm that they choose not the user. Corporate tech platforms like X can be a better fit for some survivors. X has safety tools and content moderation, making it a solid option for certain individuals. Grok can be a big help for survivors looking for resources or support! As a survivor, you know what works best for you, and safety should always come first—keep that front and center.
That said, a protocol is a game-changer for cases where the powerful are likely to censor. During China's # MeToo movement, survivors faced heavy censorship on social media platforms like Weibo and WeChat, where posts about sexual harassment were quickly removed, and hashtags like # MeToo or "woyeshi" were blocked by government and platform filters. To bypass this, activists turned to blockchain technology encoding their stories—like Yue Xin’s open letter about a Peking University case—into transaction metadata. This made the information tamper-proof and publicly accessible, resisting censorship since blockchain data can’t be easily altered or deleted.
I posted this on X 2/28/25. I wanted to try my first long post on a nostr client. The Epstein cover up is ongoing so it’s still relevant, unfortunately.
If you are a survivor or loved one who is reading this and needs support please reach out to: National Sexual Assault Hotline 24/7 https://rainn.org/
Hours: Available 24 hours
-
 @ c9badfea:610f861a
2025-05-25 22:36:12
@ c9badfea:610f861a
2025-05-25 22:36:12- Install Notally (it's free and open source)
- Open the app, tap ≡, and select Settings
- Tap View and switch to Grid
- Return to the main screen
- Tap ☑ to create a task list and ✏️ to create a note
- Enjoy!
ℹ️ You can also add pictures and set reminders for notes and task lists
ℹ️ Add labels to the notes (e.g. "Diary", "Snippet" or "Knowledge")
ℹ️ Use emojis to enhance titles (e.g. "🛒 Purchases" and "🔗️ Links")
-
 @ 7f6db517:a4931eda
2025-05-27 04:01:31
@ 7f6db517:a4931eda
2025-05-27 04:01:31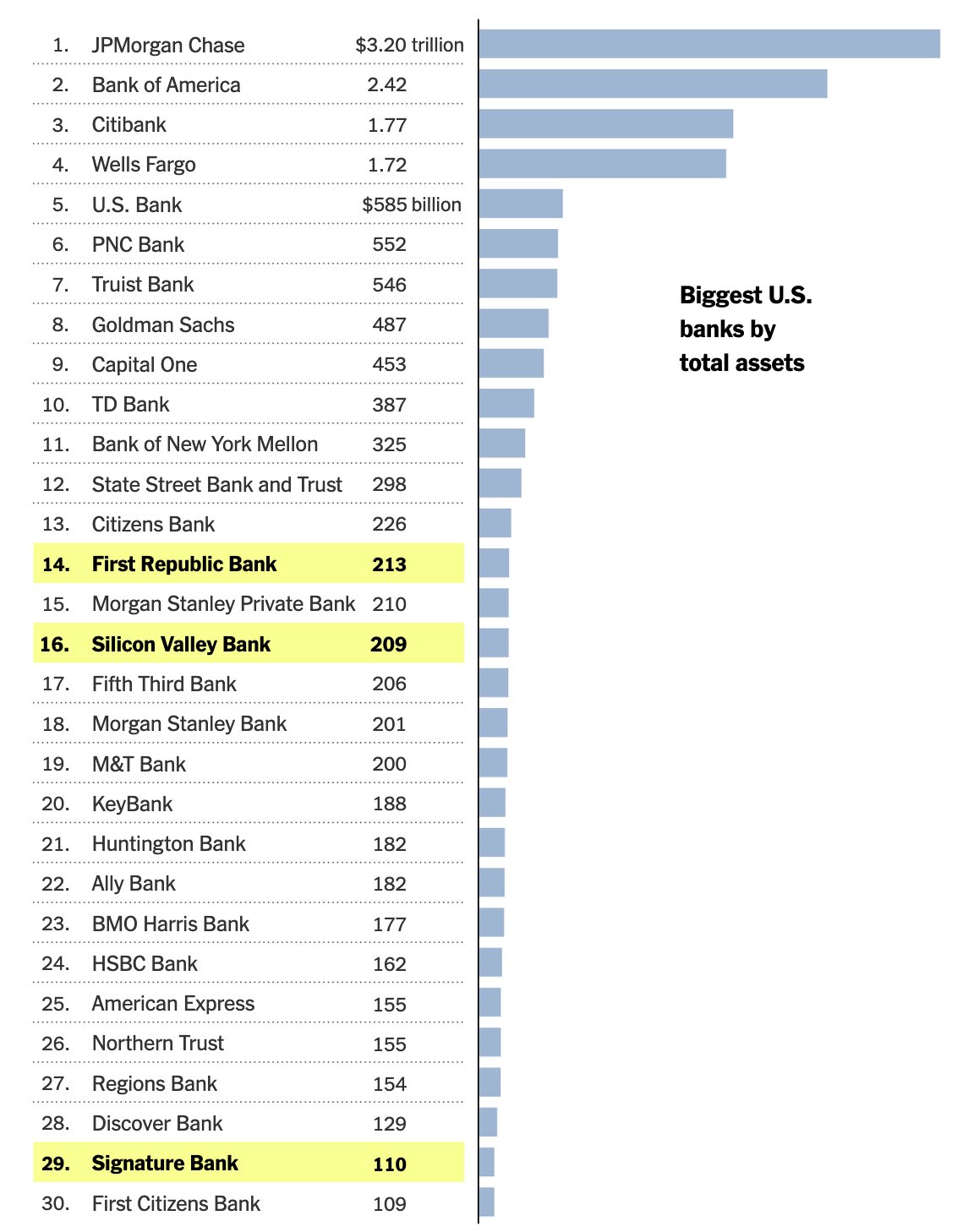
Bank run on every crypto bank then bank run on every "real" bank.
— ODELL (@ODELL) December 14, 2022
Good morning.
It looks like PacWest will fail today. It will be both the fifth largest bank failure in US history and the sixth major bank to fail this year. It will likely get purchased by one of the big four banks in a government orchestrated sale.
March 8th - Silvergate Bank
March 10th - Silicon Valley Bank
March 12th - Signature Bank
March 19th - Credit Suisse
May 1st - First Republic Bank
May 4th - PacWest Bank?PacWest is the first of many small regional banks that will go under this year. Most will get bought by the big four in gov orchestrated sales. This has been the playbook since 2008. Follow the incentives. Massive consolidation across the banking industry. PacWest gonna be a drop in the bucket compared to what comes next.
First, a hastened government led bank consolidation, then a public/private partnership with the remaining large banks to launch a surveilled and controlled digital currency network. We will be told it is more convenient. We will be told it is safer. We will be told it will prevent future bank runs. All of that is marketing bullshit. The goal is greater control of money. The ability to choose how we spend it and how we save it. If you control the money - you control the people that use it.
If you found this post helpful support my work with bitcoin.

-
 @ 8671a6e5:f88194d1
2025-05-25 20:38:25
@ 8671a6e5:f88194d1
2025-05-25 20:38:25#### Dit is een reactie op dit artikel Dit is een reactie op dit artikel\ --\ Geachte redactie van De Tijd,
Met teleurstelling las ik uw recente artikel waarin Bitcoin onterecht wordt omschreven als een "hot wallet", en waarin de meldplicht voor de fiscus onnauwkeurig wordt voorgesteld.\ Maar wat vooral schrijnend is (naast het gebrek aan kennis inzake Bitcoin) is de lichte zweem van "onbehagen" die er omheen werd geweven.
Bitcoin is geen hot wallet, maar een gedecentraliseerd netwerk met bewezen digitale schaarste – hard money. Een "hot wallet" is eenvoudig gezegd een internet-verbonden opslagmethode voor bitcoin, zoals een app op een smartphone, terwijl een cold wallet offline private sleutels bewaart. Dit onderscheid is essentieel voor correcte berichtgeving, maar werd helaas onvoldoende uitgelegd aan uw lezers.
Daarnaast schetst het artikel een misleidend beeld van de meldplicht. \ Volgens de Belgische wetgeving moeten Belgische belastingplichtigen buitenlandse rekeningen melden bij het CAP en jaarlijks in hun belastingaangifte. De juridische status van zulke exchange in de EU-"junta" zone, is daarbij van belang. Dat werd in het artikel gewoon onder de mat geveegd zonder enige nuance.\ \ De Belgische fiscus biedt na zestien jaar trouwens nog steeds geen adequate manier om bitcoin bezit correct aan te geven, zoals een veld voor xpub- of zpub-sleutels (mensen die dit correct willen aangeven worden geconfronteerd met een gebrek aan kennis die overal in België op eenzelfde bedroevend laag niveau zit,... hier hebben we al vaker voorbeelden van gezien).\ \ Vertrouwen op zulke instanties om je cold-storage holdings te melden, is vragen om problemen. Toch meldt uw krant dat je dat maar beter WEL doet.\ Er is echter GEEN verplichting om non-custodial wallets aan te tegen. Het gaat hier voor alle duidelijkheid over bitcoin UTXO's waar de houder zelf in het bezit is van de eigen sleutels, ... echte bitcoin dus:)... \ Zulk hard money spontaan melden bij een instantie die daar niet klaar voor is, kan onnodige administratieve lasten opleggen zonder juridische basis en bovendien ook andere problemen veroorzaken. \ Dit advies van De Tijd, lijkt eerder ingegeven door overdreven voorzichtigheid, dan dan door een wettelijke verplichting. Maar vooral moet het een sfeertje scheppen alsof alle bitcoin houders die NIET via een gecapteerde derde partij werken (een exchange of een service) blijkbaar "louche" zijn. \ Dan kunnen we meteen ook iedereen die een waardevol schilderij in de privé woning heeft hangen "louche" noemen, om maar te zwijgen over fake-NGO's en dure wijn collecties niet?
Uw artikel schept naast het etaleren van een gebrek aan kennis inzake bitcoin, bovendien een sfeer van criminalisering, waarbij uw artikel gewag maakt van het oude refrein: “Wie niets te verbergen heeft...” \ Komaan, dit argument is intussen doorzichtig en dient enkel om mensen bang te maken en totalitaire controle als ‘normaal’ te doen aanvaarden. \ Net zoals de wildgroei aan flitspalen en de in oktober uit te rollen CBDC "Digitale Euro", die in essentie een programmeerbare, makkelijk uitschakelbare nep-euro zal zijn (een slechtere vorm van een kermis-jeton).
Het blijft vreemd dat er in De Tijd – net als bij andere mainstream media – zelden of nooit ruimte is voor een kritische stem hierover... het zal niet in de kraam passen.\ Net zoals het niet in de kraam past om de lamentabele BEL20 performantie of de laakbare promotie van rommel-aandelen op TV aan de kaak te stellen, of de huizenmarkt-zwendel eens een welverdiende kritiek te geven. Kritiek of nuances hierover zijn ook ... uit den boze.\ Neen, bij De Tijd gaan we het altijd op veilig spelen, en de paar mensen die de krant nog betalend lezen vooral niet wijzer maken?\ \ Er was nochtans goede hoop op meer en betere berichtgeven over bitcoin. Maar die hoop smelt zienderogen weg.
Het artikel plaatst bitcoin gebruikers impliciet in het kamp van potentiële overtreders, wat bijdraagt aan een negatieve en onterechte criminalisering. \ Dit patroon, ook zichtbaar in media zoals De Morgen en De Standaard, vertroebelt elementaire kennis en benadeelt uw betalende abonnees door hen foutieve en onvolledige informatie te verstrekken over het best presterende activum van het afgelopen decennium – en over de unieke rol van bitcoin als alternatief voor de steeds verder wegsmeltende koopkracht en waarde van fiat-munten van oude staten en unies.
Ik hoop dat u uw verantwoordelijkheid opneemt om abonnees objectief en feitelijk correct te informeren, zodat zij de échte opportunity cost van hun keuzes kunnen inschatten – een kost die, ironisch genoeg, met elk jaarabonnement verder oploopt.
Wie sinds 2015 maandelijks €50 aan bitcoin had gekocht in plaats van een abonnement op De Tijd te nemen, heeft zich alvast niet laten misleiden door uw doemverhalen en onjuiste informatie over dit activum. En het verschil in rendement is, op z’n zachtst gezegd, significant.
Jammer maar helaas, "De Tijd" lijkt anno 2025 nog steeds niet in staat om systematisch correct te berichten over "de" Bitcoin.\ \ Een paar Anonieme Bitcoiners
-
 @ 1d7ff02a:d042b5be
2025-05-27 02:56:33
@ 1d7ff02a:d042b5be
2025-05-27 02:56:33ສຳລັບໃຜທີ່ຍັງບໍ່ເຂົ້າໃຈ Bitcoin ຢ່າງແທ້ຈິງ, ຫມາຍຄວາມວ່າເຈົ້າຍັງບໍ່ທັນເຂົ້າໃຈວ່າເງິນແມ່ນຫຍັງ, ໃຜເປັນຜູ້ສ້າງມັນ, ແລະເປັນຫຍັງມະນຸດຈຶ່ງຕ້ອງການເງິນ. ມັນເປັນເລື່ອງ scam ທີ່ລະບົບການສຶກສາບໍ່ໄດ້ສອນເລື່ອງສຳຄັນນີ້, ໃນຂະນະທີ່ພວກເຮົາໃຊ້ເວລາເກືອບທັງຊີວິດເພື່ອຫາເງິນ. ດັ່ງນັ້ນ, ຂໍແນະນຳໃຫ້ follow the money ແລະ ສຶກສາ Bitcoin ຢ່າງຈິງຈັງ.
Why Bitcoin Matters
Saving is the greatest discovery in human history
ກ່ອນທີ່ມະນຸດຈະຮຽນຮູ້ການເກັບອອມ, ພວກເຮົາເປັນພຽງແຕ່ສັດທີ່ມີຊີວິດຢູ່ແບບວັນຕໍ່ວັນ. ການປະຢັດແມ່ນສິ່ງທີ່ເຮັດໃຫ້ມະນຸດແຕກຕ່າງຈາກສັດອື່ນ — ຄວາມສາມາດໃນການຄິດກ່ຽວກັບອະນາຄົດ ແລະ ເກັບໄວ້ສຳລັບມື້ຫຼັງ.
Saving created civilization itself
ບໍ່ມີການເກັບອອມ, ບໍ່ມີການສ້າງເມືອງ, ບໍ່ມີວິທະຍາສາດ, ບໍ່ມີສິລະປະ. ທຸກສິ່ງທີ່ເຮົາເອີ້ນວ່າ "ຄວາມກ້າວໜ້າ" ແມ່ນມາຈາກຄວາມສາມາດໃນການຮູ້ຈັກເກັບອອມ.
Money is the greatest creation in human history
ມັນເປັນເຄື່ອງມືທີ່ເຮັດໃຫ້ອາລະຍະທຳມະນຸດກ້າວໜ້າມາເຖິງທຸກມື້ນີ້ ເງິນ ເປັນເຄື່ອງມືທີ່ດີທີ່ສຸດທີ່ມະນຸດໃຊ້ໃນການເກັບອອມ.
Bitcoin is the best money ever created
ມັນແມ່ນເງິນທີ່ສົມບູນແບບທີ່ສຸດທີ່ມະນຸດເຄີຍສ້າງຂຶ້ນມາ. ບໍ່ມີໃຜສາມາດ ຄວບຄຸມ, ຈັດການ, ທຳລາຍ ແລະ ມີຈຳກັດຢ່າງແທ້ຈິງ ຄືກັບເວລາໃນຊີວິດ.
Bitcoin ຄືກັບ black hole
ທີ່ຈະດູດເອົາມູນຄ່າທັງໝົດຈາກລະບົບການເງິນທີ່ເສຍຫາຍມັນຈະດູດເອົາຄວາມໝັ້ນຄົງແລະມູນຄ່າມາສູ່ຕົວມັນເອງ. ທຸກສິ່ງທີ່ມີມູນຄ່າຈະໄຫຼເຂົ້າສູ່ Bitcoin ໃນທີ່ສຸດ.
Bitcoin ຄືກັບສາດສະໜາພຸດທີ່ຄົ້ນພົບຄວາມຈິງ
ມັນເຮັດໃຫ້ເຂົ້າໃຈຕົ້ນຕໍບັນຫາຂອງລະບົບການເງິນປະຈຸບັນ ແລະ ເກີດເປັນບັນຫາຫລາຍໆຢ່າງໃນສັງຄົມ ດັ່ງກັບພະພຸດທະເຈົ້າທີ່ເຂົ້າໃຈທຸກ ແລະ ເຫດຂອງການເກີດທຸກ.
Bitcoin ຄືອິດສະຫຼະພາບ
ເງິນຄືອຳນາດ, ເງິນຄືສິ່ງຄວບຄຸມພຶດຕິກຳຂອງມະນຸດ ເມື່ອເຮົາມີເງິນທີ່ຮັກສາມູນຄ່າໄດ້ ແລະ ຄວບຄຸມບໍ່ໄດ້ ຈຶ່ງຈະມີຄວາມອິດສະຫຼະທາງຄວາມຄິດ, ການສະແດງອອກ, ແລະ ອຳນາດໃນການເລືອກ.
ຫນີ້ສິນທີ່ມະນຸດສ້າງຂຶ້ນໃນປະຈຸບັນນີ້ ໃຊ້ເວລາອີກພັນປີກໍ່ໄຊ້ຫນີ້ບໍ່ໝົດ
ມັນບໍ່ມີທາງອອກ ແລະ ກຳລັງມຸ່ງໜ້າສູ່ການລົ່ມສະລາຍຢ່າງຮ້າຍແຮງ. Bitcoin ຄືແສງສະຫວ່າງທີ່ຈະຊ່ວຍປ້ອງກັນບໍ່ໃຫ້ມະນຸດເຂົ້າສູ່ຍຸກມືດມົວອີກຄັ້ງ.
Bitcoin cannot steal your time
ມັນບໍ່ສາມາດຖືກສ້າງຂຶ້ນຈາກຄວາມຫວ່າງເປົ່າ. ທຸກ Bitcoin ຕ້ອງໃຊ້ພະລັງງານແລະເວລາທີ່ແທ້ຈິງໃນການສ້າງ.
Bitcoin ຄືປະກັນໄພທີ່ປ້ອງກັນການບໍລິຫານທີ່ຜິດພາດ
ມັນຊ່ວຍປ້ອງກັນຄວາມເສື່ອມໂຊມຂອງເງິນຕາ, ເສດຖະກິດທີ່ຕົກຕ່ຳ ແລະ ນະໂຍບາຍທີ່ຜິດພາດ, Bitcoin ຈະປົກປ້ອງຄຸນຄ່າຂອງເຈົ້າ.
Bitcoin is going to absorb the world's value
ໃນທີ່ສຸດ, Bitcoin ຈະກາຍເປັນທີ່ເກັບຮັກສາມູນຄ່າຂອງໂລກທັງໝົດ. ມັນຈະດູດເອົາຄວາມມັ່ງຄັ່ງຈາກທຸກຊັບສິນ, ທຸກລາຄາ, ແລະທຸກການລົງທຶນ.
Exit The Matrix
ພວກເຮົາອາໄສຢູ່ໃນ Matrix ທາງດ້ານການເງິນ. ທຸກໆມື້ພວກເຮົາຕື່ນຂຶ້ນມາແລະໄປເຮັດວຽກ, ຄິດວ່າເຮົາກຳລັງສ້າງອະນາຄົດໃຫ້ຕົວເອງ. ແຕ່ຄວາມຈິງແລ້ວ, ພວກເຮົາພຽງແຕ່ກຳລັງໃຫ້ພະລັງງານແກ່ລະບົບທີ່ຂູດເອົາຄຸນຄ່າຈາກພວກເຮົາທຸກວິນາທີ. Bitcoin is the red pill — ມັນຈະເປີດຕາໃຫ້ເຈົ້າເຫັນຄວາມຈິງຂອງໂລກການເງິນ. Central banks are the architects of this Matrix — ພວກເຂົາສ້າງເງິນຈາກຄວາມຫວ່າງເປົ່າ, ແລະພວກເຮົາຕ້ອງເຮັດວຽກໜັກເພື່ອໄດ້ມັນມາ.
ລະບົບການສຶກສາໄດ້ຫຼອກລວງເຮົາຢ່າງໃຫຍ່ຫຼວງ. ພວກເຂົາສອນໃຫ້ເຮົາເຮັດວຽກເພື່ອຫາເງິນ, ແຕ່ບໍ່ເຄີຍສອນວ່າເງິນແມ່ນຫຍັງ. ເຮົາໃຊ້ເວລາ 12-16 ປີໃນໂຮງຮຽນ, ຫຼັງຈາກນັ້ນໃຊ້ເວລາທັງຊີວິດເພື່ອຫາເງິນ, ແຕ່ບໍ່ເຄີຍຮູ້ຈັກວ່າມັນແມ່ນຫຍັງ, ໃຜສ້າງ, ແລະເປັນຫຍັງມັນມີຄຸນຄ່າ.This is the biggest scam in human history ພວກເຮົາຖືກສອນໃຫ້ເປັນທາດຂອງລະບົບ, ແຕ່ບໍ່ໄດ້ຮັບການສອນໃຫ້ເຂົ້າໃຈລະບົບ.
The Bitcoin standard will end war
ເມື່ອບໍ່ສາມາດພິມເງິນເພື່ອສົງຄາມແລ້ວ, ສົງຄາມຈະກາຍເປັນສິ່ງທີ່ແພງເກີນໄປ.
ພວກເຮົາກຳລັງເຂົ້າສູ່ຍຸກ Bitcoin Renaissance
ຍຸກແຫ່ງການຟື້ນຟູທາງດ້ານການເງິນແລະປັນຍາ. Bitcoin is creating a new class of humans ຄົນທີ່ເຂົ້າໃຈ ແລະ ຖື Bitcoin ຈະກາຍເປັນຊົນຊັ້ນໃໝ່ທີ່ມີອິດສະຫຼະພາບຢ່າງແທ້ຈິງ.
The Path to Financial Truth
Follow the money trail ແລະເຈົ້າຈະເຫັນຄວາມຈິງ:
- ໃຜຄວບຄຸມການພິມເງິນ?
- ເປັນຫຍັງລາຄາສິນຄ້າຂຶ້ນສູງຂຶ້ນເລື້ອຍໆ?
- ເປັນຫຍັງຄົນທຸກທຸກກວ່າເກົ່າ ແລະຄົນຮັ່ງມີຮັ່ງມີກວ່າເກົ່າ?
ຄຳຕອບທັງໝົດແມ່ນຢູ່ໃນການທຳຄວາມເຂົ້າໃຈເລື່ອງເງິນ ແລະ Bitcoin.
ການສຶກສາ Bitcoin ບໍ່ແມ່ນພຽງແຕ່ການລົງທຶນ — ມັນແມ່ນການເຂົ້າໃຈອະນາຄົດຂອງເງິນຕາ ແລະ ສັງຄົມມະນຸດ.
Don't just work for money. Understand money. Study Bitcoin.
ຖ້າເຈົ້າບໍ່ເຂົ້າໃຈເງິນ, ເຈົ້າຈະເປັນທາດຂອງລະບົບຕະຫຼອດໄປ. ຖ້າເຈົ້າເຂົ້າໃຈ Bitcoin, ເຈົ້າຈະໄດ້ຮັບອິດສະຫຼະພາບ.
-
 @ 4857600b:30b502f4
2025-03-11 01:58:19
@ 4857600b:30b502f4
2025-03-11 01:58:19Key Findings
- Researchers at the University of Cambridge discovered that aspirin can help slow the spread of certain cancers, including breast, bowel, and prostate cancers
- The study was published in the journal Nature
How Aspirin Works Against Cancer
- Aspirin blocks thromboxane A2 (TXA2), a chemical produced by blood platelets
- TXA2 normally weakens T cells, which are crucial for fighting cancer
- By inhibiting TXA2, aspirin "unleashes" T cells to more effectively target and destroy cancer cells
Supporting Evidence
- Previous studies showed regular aspirin use was linked to:
- 31% reduction in cancer-specific mortality in breast cancer patients
- 9% decrease in recurrence/metastasis risk
- 25% reduction in colon cancer risk
Potential Impact
- Aspirin could be particularly effective in early stages of cancer
- It may help prevent metastasis, which causes 90% of cancer fatalities
- As an inexpensive treatment, it could be more accessible globally than antibody-based therapies
Cautions
- Experts warn against self-medicating with aspirin
- Potential risks include internal bleeding and stomach ulcers
- Patients should consult doctors before starting aspirin therapy
Next Steps
- Large-scale clinical trials to determine which cancer types and patients would benefit most
- Development of new drugs that mimic aspirin's benefits without side effects
Citations: Natural News
-
 @ 3c559080:a053153e
2025-05-25 20:26:43
@ 3c559080:a053153e
2025-05-25 20:26:43So firstly you should find an emulator for whatever you want to play on. There are many for desktop and mobile devices. Checkhere for a list of all the available consoles and their various emulators.
Next what game do you want to play? This is the like the homepage for a shit ton of roms.
Some of the more popular roms are there and other various list like Sony Nintendo
After narrowing down your selection you will end up on myrient i assume this is just some dope person hosting all these so if you get some use out of it, think of donating they even take corn, but other shitcoins too (but thats not the focus here)
Once you download the Rom of the game you want, you will get a compressed (zip) folder, unzip it and within it will be the rom, most systems will identify your emulator and use it open the game. If not, launch the emulator and within it should be an option to open a file, open the file in the unzipped folder.
Enjoy So you want to Mod?
So every Mod, is a mod for a specific game [ex. Pokemon Blue, Pokemon FireRed, Super Mario Bros.] so it requires you to get the Rom for that base game, the mod itself, and a tool to patch it.
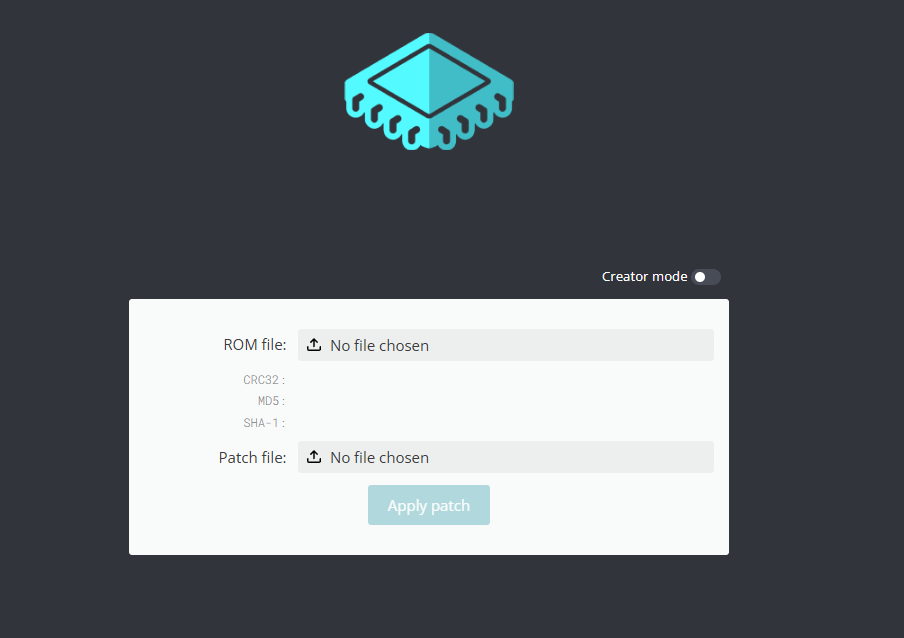 There is an online tool to easily patch the mod to the ROM. IMPORTANT, this will not change any naming, Id recommend having a folder with the base game roms, and a folder for the mods, and lastly a folder for the newly modded roms. Make sure to name or just save the game in modded roms folder after the patch.
There is an online tool to easily patch the mod to the ROM. IMPORTANT, this will not change any naming, Id recommend having a folder with the base game roms, and a folder for the mods, and lastly a folder for the newly modded roms. Make sure to name or just save the game in modded roms folder after the patch. Below are a few resource to find various Pokemon Rom mods(sometimes called hacks)
Personally, Pokemon Unbound is considered the best most polished hack. it runs on Pokemon Fire Red.
Pokemon Emerald Rouge is a cool take on the popular Rougelite genre. This runs on base game Pokemon Emerald
-
 @ 1d7ff02a:d042b5be
2025-05-27 02:35:53
@ 1d7ff02a:d042b5be
2025-05-27 02:35:53ກຸນແຈສຳຄັນແມ່ນການເຂົ້າໃຈວ່າແສງແດດບໍ່ແມ່ນສິ່ງດຽວ—ມັນແມ່ນຄື່ນຄວາມຖີ່ທີ່ສັບສົນທີ່ເຮັດວຽກຮ່ວມກັນຄືດັ່ງດົນຕີສຳລັບສຸຂະພາບຂອງມະນຸດ.
ວົງດົນຕີສຸຂະພາບຂອງດວງອາທິດ
ແສງຕອນເຊົ້າ (ແສງແດງ/ແສງອິນຟາເຣດໃກ້): ແສງແດງອ່ອນໂຍນຂອງຕອນແລງແລະຄຳ່ທີ່ປະກອບສ້າງ 90% ຂອງການປ່ອຍແສງຂອງດວງອາທິດ. ຄື່ນຄວາມຖີ່ນີ້ເຮັດໜ້າທີ່ຄືການປັບແຕ່ງເຊວລ໌, ເພີ່ມການຜະລິດພະລັງງານມີໂຕຄອນເດຍແລະກະກຽມຮ່າງກາຍຂອງທ່ານສຳລັບມື້ທີ່ຈະມາເຖິງ. ຄິດໃສ່ວ່າມັນແມ່ນການກະກຽມເຄື່ອງຈັກເຊວລ໌ຂອງທ່ານ.
ແສງຕອນກາງວັນ (ແສງ UV/ແສງສີຟ້າ): ແສງອາທິດທີ່ເຂັ້ມຂົ້ນຕອນກາງວັນສົ່ງມອບແສງອຸນຕາລະວິໂອເລດທີ່ຜະລິດວິຕາມິນ D—ຮໍໂມນທີ່ສຳຄັນຫຼາຍທີ່ເກືອບທຸກເຊວລ໌ໃນຮ່າງກາຍຂອງທ່ານມີຕົວຮັບສຳລັບມັນ. ເຖິງແມ່ນວ່າມັນຖືກເອີ້ນວ່າ "ວິຕາມິນ," ຮ່າງກາຍຂອງທ່ານຜະລິດວິຕາມິນ D ສ່ວນໃຫຍ່ຜ່ານການສຳຜັດຜິວໜັງກັບແສງ UVB. ນີ້ບໍ່ແມ່ນພຽງແຕ່ເລື່ອງສຸຂະພາບກະດູກ—ການຂາດວິຕາມິນ D ໄດ້ຖືກເຊື່ອມໂຍງກັບມະເຮັງ, ໂຣກພູມຄຸ້ມກັນຕົນເອງ, ໂຣກຫົວໃຈແລະເສັ້ນເລືອດ, ແລະການເພີ່ມຂຶ້ນຂອງການເສຍຊີວິດຈາກທຸກສາເຫດ. ວິຕາມິນ D ທີ່ຜະລິດຕາມທຳມະຊາດຈາກແສງແດດແກ່ຍາວ 2-3 ເທົ່າໃນຮ່າງກາຍຂອງທ່ານເມື່ອທຽບກັບຢາເສີມ, ສະແດງໃຫ້ເຫັນວ່າເປັນຫຍັງການສຳຜັດແສງແດດຕາມທຳມະຊາດຈຶ່ງດີກວ່າຢາເສີມ.
ແສງ UV ຍັງກະຕຸ້ນການຜະລິດເມລານິນ, ທີ່ເຮັດໜ້າທີ່ເປັນແບັດເຕີຣີທຳມະຊາດ, ເກັບຮັກສາອີເລັກຕຣອນທີ່ໃຫ້ພະລັງງານແກ່ມີໂຕຄອນເດຍຂອງທ່ານ. ໃນຂະນະທີ່ແສງສີຟ້າຮັບໃຊ້ຈຸດປະສົງຄູ່: ມັນຮັກສາໃຫ້ທ່ານຕື່ນຕົວໃນຕອນກາງວັນໃນຂະນະທີ່ຂັດຂວາງການຜະລິດເມລາໂທນິນ. ແຕ່ວ່າ, ແສງສີຟ້າມີດ້ານມືດ—ການສຶກສາສະແດງວ່າມັນສາມາດເຮັດໃຫ້ເກີດຄວາມເສຍຫາຍຂອງ DNA ແລະສ້າງສິ່ງທີ່ເປັນອັນຕະລາຍທີ່ເອີ້ນວ່າສະສາລະອົກຊິເຈນປະຕິກິລິຍາຢູ່ທັງຜິວໜັງແລະຕາ, ຄ້າຍຄືກັບລັງສີ UV. ນີ້ແມ່ນເຫດຜົນທີ່ການສຳຜັດແສງສີຟ້າໂດດດ່ຽວ (ເຊັ່ນຈາກໜ້າຈໍ) ໂດຍບໍ່ມີຄື່ນຄວາມຖີ່ປ້ອງກັນຂອງແສງອາທິດສາມາດເປັນອັນຕະລາຍໂດຍສະເພາະ.
ການປ່ຽນແປງຕອນແລງ: ເມື່ອແສງສີຟ້າຫຼຸດລົງໃນຕອນແລງ, ຮ່າງກາຍຂອງທ່ານເລີ່ມຜະລິດເມລາໂທນິນ, ທີມງານທຳຄວາມສະອາດເຊວລ໌ທີ່ເອົາຜະລິດຕະພັນພິດທີ່ສະສົມໃນລະຫວ່າງການຜະລິດພະລັງງານຂອງມື້ອອກ.
ວິກິດການແສງສະໄໝໃໝ່
ມະນຸດສະໄໝໃໝ່ໃຊ້ເວລາ 93% ຢູ່ໃນເຮືອນ, ສ້າງຄວາມບໍ່ສົມດູນຂອງແສງທີ່ເປັນອັນຕະລາຍ. ພວກເຮົາໄດ້ປ່ຽນໝໍ້ແສງໄຟແກ້ວທີ່ມີປະໂຫຍດດ້ວຍ LED ທີ່ຂາດຄື່ນຄວາມຖີ່ແສງອິນຟາເຣດໃກ້ທີ່ປ້ອງກັນ, ໃນຂະນະທີ່ແສງສີຟ້າປອມຈາກໜ້າຈໍຂັດຂວາງການຜະລິດເມລາໂທນິນຕາມທຳມະຊາດຂອງພວກເຮົາໃນຕອນກາງຄືນ. ນີ້ສ້າງພາຍຸທີ່ສົມບູນແບບ: ຄວາມເຄັ່ງຕຶງຈາກການເກີດອົກຊິເດຊັນໂດຍບໍ່ມີກົນໄກການທຳຄວາມສະອາດຕາມທຳມະຊາດ, ການຂາດວິຕາມິນ D, ແລະການຂາດຄື່ນຄວາມຖີ່ປ້ອງກັນຕອນເຊົ້າທີ່ກະກຽມຮ່າງກາຍຂອງພວກເຮົາສຳລັບການສຳຜັດແສງແດດ.
ທາງແກ້ໄຂຕາມທຳມະຊາດ
ການຄົ້ນຄວ້າຊີ້ໃຫ້ເຫັນວິທີການງ່າຍໆ: ຮັບເອົາຈັງຫວະຕາມທຳມະຊາດຂອງດວງອາທິດ. ເລີ່ມມື້ຂອງທ່ານດ້ວຍການສຳຜັດແສງຕອນເຊົ້າເພື່ອກະກຽມມີໂຕຄອນເດຍຂອງທ່ານ. ຍອມຮັບວ່າແສງແດດຕອນກາງວັນບາງຢ່າງໃຫ້ວິຕາມິນ D ແລະເມລານິນທີ່ຈຳເປັນ. ຄ່ອຍໆຜ່ອນຄາຍເມື່ອແສງແລງຫຼຸດລົງ, ອະນຸຍາດໃຫ້ມີການຜະລິດເມລາໂທນິນຕາມທຳມະຊາດ.
ຮ່າງກາຍຂອງທ່ານພັດທະນາມາຫຼາຍລ້ານປີກັບວົງຈອນແສງນີ້. ໃນຂະນະທີ່ພວກເຮົາບໍ່ສາມາດປະຖິ້ມຊີວິດທີ່ທັນສະໄໝໄດ້, ພວກເຮົາສາມາດເຄົາລົບຄວາມຕ້ອງການທາງຊີວະວິທະຍາຂອງພວກເຮົາສຳລັບແສງແດດແບບຄົບຖ້ວນ. ຫຼັງຈາກທັງໝົດ, ທຸກເຊວລ໌ໃນຮ່າງກາຍຂອງທ່ານແລ່ນດ້ວຍພະລັງງານ, ແລະດວງອາທິດຍັງຄົງເປັນແຫຼ່ງພະລັງງານຫຼັກຂອງໂລກພວກເຮົາ. ໃນໂລກເທັກໂນໂລຢີສູງຂອງພວກເຮົາ, ພວກເຮົາຕ້ອງຈື່ຄູ່ຮ່ວມງານບູຮານລະຫວ່າງສຸຂະພາບຂອງມະນຸດກໍຄືແສງແດດ.
-
 @ 502ab02a:a2860397
2025-05-27 01:45:49
@ 502ab02a:a2860397
2025-05-27 01:45:49เราค่อยๆลำดับเรื่องราวเริ่มจากเบาๆกันก่อนนะครับ หากย้อนกลับไปในปี 2009 บนเส้นทางที่โลกกำลังสับสนระหว่างการกินที่อิงธรรมชาติกับแนวทางการเปลี่ยนแปลงอาหารแบบสุดขั้ว Ethan Brown ได้ก่อตั้งบริษัท Beyond Meat ขึ้นมา โดยมีจุดประสงค์ชัดเจนว่าอยากสร้าง "เนื้อจากพืช" ให้มีรสชาติ เนื้อสัมผัส และประสบการณ์ที่ใกล้เคียงกับเนื้อสัตว์จริงให้มากที่สุดเท่าที่จะทำได้ นี่คือภาพลวงตาที่ถูกสร้างขึ้นภายใต้ธงของความยั่งยืน แต่เบื้องลึกกลับแฝงความเงียบงันอยู่ใต้เงาเทคโนโลยี
Ethan Brown ไม่ใช่คนที่ตื่นเช้ามาแล้วอยากเปลี่ยนโลกในทันที เขาเติบโตมากับพ่อที่เป็นนักอนุรักษ์ธรรมชาติ มีฟาร์มโคนมเล็ก ๆ ให้ได้สัมผัสความจริงของเกษตรกรรมแบบดั้งเดิม เขาเรียนจบปริญญาตรีด้านประวัติศาสตร์และรัฐบาล ต่อด้วยปริญญาโทด้านนโยบายสาธารณะจาก University of Maryland และ MBA จาก Columbia University เขาเคยทำงานด้านนโยบายพลังงานทางเลือกที่ National Governors Association และบริษัท Ballard Power Systems ก่อนจะย้ายขั้วจากพลังงานสู่โปรตีนแทน
ช่วงหนึ่งเขาพูดใน TED ว่า “ผมมองเห็นว่าอาหารนั้นเชื่อมโยงกับสิ่งแวดล้อมและสุขภาพมนุษย์อย่างลึกซึ้ง แต่เราแทบไม่พูดถึงเรื่องนี้ในระดับระบบเลย” เขาเห็นว่าสัตว์คือ “เครื่องจักรแปลงโปรตีนจากพืชไปเป็นเนื้อ” ซึ่งเขาเชื่อว่ามัน “ไม่จำเป็นอีกต่อไปแล้ว” ในศตวรรษที่ 21
Beyond Meat ไม่ได้ใช้สูตรการต้มถั่วแล้วปั้นเป็นเบอร์เกอร์แบบบ้าน ๆ แต่ใช้กระบวนการแปรรูปที่ซับซ้อนระดับอุตสาหกรรมที่เรียกว่า High Moisture Extrusion (HME) ที่ต้องใช้เครื่องจักรเฉพาะราคาแพงมาก เพื่อดัดแปลงโปรตีนพืช เช่น ถั่วเหลือง ถั่วลันเตา ให้มีโครงสร้างเหมือนกล้ามเนื้อสัตว์ ทั้งเส้นใย ความชุ่มฉ่ำ และแรงต้านเมื่อกัด ซึ่งทั้งหมดนี้ไม่สามารถทำในครัวชาวบ้านได้ง่าย ๆ
บริษัทได้รับทุนสนับสนุนตั้งแต่ช่วงเริ่มต้นจากกลุ่มนักลงทุนที่มีอิทธิพลใน Silicon Valley เช่น Kleiner Perkins และ Obvious Corporation ของ Evan Williams ผู้ร่วมก่อตั้ง Twitter ก่อนจะขยายฐานนักลงทุนไปยัง Tyson Foods (ซึ่งเป็นบริษัทยักษ์ใหญ่ด้านเนื้อสัตว์ของสหรัฐฯ ที่ลงทุนใน Beyond Meat ก่อนจะถอนตัวภายหลัง) และนักแสดงฮอลลีวูดอย่าง Leonardo DiCaprio การเข้าระดมทุนในตลาดหุ้น (IPO) ปี 2019 ก็ยิ่งสร้างกระแสให้บริษัทกลายเป็นภาพตัวแทนของการกินอนาคตที่ยั่งยืน ทว่าในความหรูหรานั้น มีรอยร้าวแฝงอยู่เสมอ
ในขณะที่ภาพจำของ Beyond Meat ถูกวาดว่าเป็น “ทางรอดของโลก” และ “อาหารเพื่อสิ่งแวดล้อม” รัฐบาลสหรัฐฯ ก็สนับสนุนทิศทางนี้อย่างเงียบเชียบ ด้วยการอัดงบประมาณกว่า 125 ล้านดอลลาร์เข้าสู่อุตสาหกรรมโปรตีนทางเลือกผ่านโครงการต่าง ๆ เช่น หน่วยงานวิจัย USDA และกองทุนสนับสนุนมหาวิทยาลัยด้านเทคโนโลยีอาหาร ไม่ต่างจากรัฐบาลอิสราเอลที่ทุ่มงบกว่า 18 ล้านดอลลาร์ให้บริษัทเนื้อเพาะเลี้ยงแบบไม่มีอ้อมค้อม ทั้งหมดนี้กำลังสร้างระบบอาหารที่ไม่ต้องพึ่งดิน ไม่ต้องพึ่งแดด ไม่ต้องพึ่งเกษตรกร แต่ขึ้นอยู่กับโรงงานที่ควบคุมโดยบริษัทมหาชนเพียงไม่กี่เจ้า
เมื่อมองให้ลึกลงไป Beyond Meat ไม่ใช่แค่บริษัทอาหาร แต่คือจุดเริ่มต้นแรกๆของโลก ในด้านระบบนิเวศใหม่ที่ตัด “คนตัวเล็ก” ออกจากสมการเกษตรกรรมโดยสิ้นเชิง เกษตรกรจะไม่มีทางผลิต “เนื้อจากพืช” เหล่านี้ได้ด้วยตัวเอง เพราะต้องใช้เทคโนโลยีราคาแพง วัตถุดิบเฉพาะ และสูตรการแปรรูปที่ถูกจดสิทธิบัตรไว้หมดแล้ว ระบบอาหารจึงค่อย ๆ ถูกปิดตายภายใต้รั้วของลิขสิทธิ์ เหมือนโลกของซอฟต์แวร์ที่ไม่มีใครแตะต้องโค้ดต้นฉบับได้ ทุกคำที่เคี้ยวอาจกลายเป็นทรัพย์สินของใครบางคน และในวันที่ดินผืนสุดท้ายไม่ได้ปลูกพืช แต่กลายเป็นโรงงานสังเคราะห์โปรตีน นั่นแหละที่มนุษย์จะพบว่า ตนเองไม่ได้เป็น “ผู้ผลิตอาหาร” อีกต่อไป แต่กลายเป็น “ผู้บริโภค” ตลอดกาล
แม้ตัวเลขยอดขายของ Beyond Meat จะพุ่งขึ้นในช่วงแรกหลังเข้าตลาดหุ้น แต่เมื่อเวลาผ่านไป กลับสะท้อนความจริงที่น่าสนใจว่าสิ่งที่ดูเหมือนจะเป็นทางออกของโลก อาจไม่ใช่คำตอบที่ยั่งยืนเลยก็ได้
ในปี 2022 บริษัทประกาศลดพนักงานลง 19% และราคาหุ้นร่วงลงกว่า 80% จากจุดสูงสุด พร้อมกับข่าวคราวที่ส่อให้เห็นปัญหาด้านความปลอดภัยในสายการผลิต และยอดขายที่ไม่เติบโตตามเป้า แม้จะพยายามขยายตลาดอย่างต่อเนื่อง แต่คนทั่วไปเริ่มตระหนักว่า “เนื้อจากพืช” ที่แปรรูปหนักอาจไม่ใช่คำตอบของสุขภาพหรือสิ่งแวดล้อมอย่างที่เคยเชื่อ
ไม่เพียงเท่านั้น ผลการสำรวจในอเมริกาและยุโรปเริ่มชี้ว่า คนที่เคยทดลองกิน plant-based meat กลับไม่ซื้อซ้ำ โดยให้เหตุผลว่าไม่อร่อย แพง และไม่เชื่อว่าเป็นอาหารที่ดีต่อร่างกายจริง ๆ อีกทั้งบางรายถึงกับบอกว่ารู้สึกแปลกแยก เพราะอาหารที่มีส่วนผสมเยอะและชื่อส่วนประกอบที่อ่านไม่ออก มักทำให้คนรู้สึกว่าไม่ใช่อาหารธรรมชาติ ซึ่งขัดกับความตั้งใจเดิมที่อยากกินอาหารเพื่อสุขภาพ
คำว่า “ยั่งยืน” จึงไม่เพียงพอจะอธิบายได้ว่าอะไรคือสิ่งดีจริง ๆ เพราะหากความยั่งยืนนั้นหมายถึงการผูกขาด แปรรูป และบังคับให้ผู้คนต้องซื้ออาหารจากบริษัทไม่กี่แห่ง มันก็ไม่ได้ต่างอะไรกับการจำกัดอิสรภาพในจานข้าว อาหารที่แท้ควรเป็นของทุกคน เป็นสิทธิ์พื้นฐานที่มนุษย์ควรสร้างได้เอง ไม่ใช่ต้องลงทะเบียนซื้อกับห้างใหญ่ ๆ ผ่าน QR code ทุกมื้อ
ทุกวันนี้ Beyond Meat ยังไม่ถึงจุดตกต่ำที่สุด และยังมีโอกาสกลับมาได้เสมอ แต่สิ่งนึงที่เราต้องตระหนักเอาไว้คือ นี่ยังเป็นแค่ยักษ์เล็กไม่ใช่ยักษ์ใหญ่ เทคโนโลยีการสกัดโปรตีนพืชมาขยำเป็นรูปนั้น ณ วินาทีนี้ คือโบราณเกินไปแล้วครับ ในตลาดก็มีหมูปลอมเนื้อปลอมแบบนี้ออกมามากมาย หน้าตางดงามสมจริง แต่สิ่งเหล่านี้มันคือแค่จุดเริ่มต้นครับ ถ้าจะนับเรื่องราวเหล่านี้ว่าเริ่มจาก 2009 ก็ไม่ผิดนัก
เมื่อถึงจุดหนึ่ง คุณจะมองเห็นลำดับชั้นของ ธุรกิจ นวตกรรม การครอบงำทางการตลาดแบบผูกมัดที่ตัดแขนตัดขาไปทีละนิดจนเราหมดสิทธิ์เลือก สิ่งเดียวที่เราจะเลือกได้คือ ซื้อเนื้อจากแลปไหน #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 4857600b:30b502f4
2025-03-10 12:09:35
@ 4857600b:30b502f4
2025-03-10 12:09:35At this point, we should be arresting, not firing, any FBI employee who delays, destroys, or withholds information on the Epstein case. There is ZERO explanation I will accept for redacting anything for “national security” reasons. A lot of Trump supporters are losing patience with Pam Bondi. I will give her the benefit of the doubt for now since the corruption within the whole security/intelligence apparatus of our country runs deep. However, let’s not forget that probably Trump’s biggest mistakes in his first term involved picking weak and easily corruptible (or blackmailable) officials. It seemed every month a formerly-loyal person did a complete 180 degree turn and did everything they could to screw him over, regardless of the betrayal’s effect on the country or whatever principles that person claimed to have. I think he’s fixed his screening process, but since we’re talking about the FBI, we know they have the power to dig up any dirt or blackmail material available, or just make it up. In the Epstein case, it’s probably better to go after Bondi than give up a treasure trove of blackmail material against the long list of members on his client list.
-
 @ c9badfea:610f861a
2025-05-25 19:40:48
@ c9badfea:610f861a
2025-05-25 19:40:48- Install Currencies (it's free and open source)
- Launch the app, tap ⋮ and select Settings
- Enable the Foreign Transaction Fee to factor in conversion fees if necessary
- Tap Data Provider and choose another provider if necessary
- Enjoy ad-free conversion rates
ℹ️ Tap 📈 to open the exchange rate chart
-
 @ 6389be64:ef439d32
2025-02-27 21:32:12
@ 6389be64:ef439d32
2025-02-27 21:32:12GA, plebs. The latest episode of Bitcoin And is out, and, as always, the chicanery is running rampant. Let’s break down the biggest topics I covered, and if you want the full, unfiltered rant, make sure to listen to the episode linked below.
House Democrats’ MEME Act: A Bad Joke?
House Democrats are proposing a bill to ban presidential meme coins, clearly aimed at Trump’s and Melania’s ill-advised token launches. While grifters launching meme coins is bad, this bill is just as ridiculous. If this legislation moves forward, expect a retaliatory strike exposing how politicians like Pelosi and Warren mysteriously amassed their fortunes. Will it pass? Doubtful. But it’s another sign of the government’s obsession with regulating everything except itself.
Senate Banking’s First Digital Asset Hearing: The Real Target Is You
Cynthia Lummis chaired the first digital asset hearing, and—surprise!—it was all about control. The discussion centered on stablecoins, AML, and KYC regulations, with witnesses suggesting Orwellian measures like freezing stablecoin transactions unless pre-approved by authorities. What was barely mentioned? Bitcoin. They want full oversight of stablecoins, which is really about controlling financial freedom. Expect more nonsense targeting self-custody wallets under the guise of stopping “bad actors.”
Bank of America and PayPal Want In on Stablecoins
Bank of America’s CEO openly stated they’ll launch a stablecoin as soon as regulation allows. Meanwhile, PayPal’s CEO paid for a hat using Bitcoin—not their own stablecoin, Pi USD. Why wouldn’t he use his own product? Maybe he knows stablecoins aren’t what they’re hyped up to be. Either way, the legacy financial system is gearing up to flood the market with stablecoins, not because they love crypto, but because it’s a tool to extend U.S. dollar dominance.
MetaPlanet Buys the Dip
Japan’s MetaPlanet issued $13.4M in bonds to buy more Bitcoin, proving once again that institutions see the writing on the wall. Unlike U.S. regulators who obsess over stablecoins, some companies are actually stacking sats.
UK Expands Crypto Seizure Powers
Across the pond, the UK government is pushing legislation to make it easier to seize and destroy crypto linked to criminal activity. While they frame it as going after the bad guys, it’s another move toward centralized control and financial surveillance.
Bitcoin Tools & Tech: Arc, SatoChip, and Nunchuk
Some bullish Bitcoin developments: ARC v0.5 is making Bitcoin’s second layer more efficient, SatoChip now supports Taproot and Nostr, and Nunchuk launched a group wallet with chat, making multisig collaboration easier.
The Bottom Line
The state is coming for financial privacy and control, and stablecoins are their weapon of choice. Bitcoiners need to stay focused, keep their coins in self-custody, and build out parallel systems. Expect more regulatory attacks, but don’t let them distract you—just keep stacking and transacting in ways they can’t control.
🎧 Listen to the full episode here: https://fountain.fm/episode/PYITCo18AJnsEkKLz2Ks
💰 Support the show by boosting sats on Podcasting 2.0! and I will see you on the other side.
-
 @ c1e6505c:02b3157e
2025-05-27 01:11:45
@ c1e6505c:02b3157e
2025-05-27 01:11:45I spent Memorial Day swimming in the local river - something I try to do at least four times a week. It’s the best form of exercise imo, but it’s more than that. Swimming against the tide, feeling the water move around me... there’s something about it that keeps me grounded. Nature at her peak.
Today I brought my X-Pro2 with the 1959 Leica Summaron 35mm f/2.8. I'm still testing the lens wide open to get a feel for its character. My subject this time: the light playing on the ripples and waves.
While I was shooting, a kid randomly ran up to me and started telling me something about what he got for his dad while fishing, or something - I didn’t quite hear him - and then he asked what I was looking at. I told him, “The ripples. The way the light is refracting.” I had him sit exactly where I was so he could see it too.
He lit up. You could tell no one had ever pointed something like that out to him before. In that moment, I felt like maybe I was able to plant a little seed - a new way of seeing.
This is what I was looking at.

-
 @ 94a6a78a:0ddf320e
2025-02-19 21:10:15
@ 94a6a78a:0ddf320e
2025-02-19 21:10:15Nostr is a revolutionary protocol that enables decentralized, censorship-resistant communication. Unlike traditional social networks controlled by corporations, Nostr operates without central servers or gatekeepers. This openness makes it incredibly powerful—but also means its success depends entirely on users, developers, and relay operators.
If you believe in free speech, decentralization, and an open internet, there are many ways to support and strengthen the Nostr ecosystem. Whether you're a casual user, a developer, or someone looking to contribute financially, every effort helps build a more robust network.
Here’s how you can get involved and make a difference.
1️⃣ Use Nostr Daily
The simplest and most effective way to contribute to Nostr is by using it regularly. The more active users, the stronger and more valuable the network becomes.
✅ Post, comment, and zap (send micro-payments via Bitcoin’s Lightning Network) to keep conversations flowing.\ ✅ Engage with new users and help them understand how Nostr works.\ ✅ Try different Nostr clients like Damus, Amethyst, Snort, or Primal and provide feedback to improve the experience.
Your activity keeps the network alive and helps encourage more developers and relay operators to invest in the ecosystem.
2️⃣ Run Your Own Nostr Relay
Relays are the backbone of Nostr, responsible for distributing messages across the network. The more independent relays exist, the stronger and more censorship-resistant Nostr becomes.
✅ Set up your own relay to help decentralize the network further.\ ✅ Experiment with relay configurations and different performance optimizations.\ ✅ Offer public or private relay services to users looking for high-quality infrastructure.
If you're not technical, you can still support relay operators by subscribing to a paid relay or donating to open-source relay projects.
3️⃣ Support Paid Relays & Infrastructure
Free relays have helped Nostr grow, but they struggle with spam, slow speeds, and sustainability issues. Paid relays help fund better infrastructure, faster message delivery, and a more reliable experience.
✅ Subscribe to a paid relay to help keep it running.\ ✅ Use premium services like media hosting (e.g., Azzamo Blossom) to decentralize content storage.\ ✅ Donate to relay operators who invest in long-term infrastructure.
By funding Nostr’s decentralized backbone, you help ensure its longevity and reliability.
4️⃣ Zap Developers, Creators & Builders
Many people contribute to Nostr without direct financial compensation—developers who build clients, relay operators, educators, and content creators. You can support them with zaps! ⚡
✅ Find developers working on Nostr projects and send them a zap.\ ✅ Support content creators and educators who spread awareness about Nostr.\ ✅ Encourage builders by donating to open-source projects.
Micro-payments via the Lightning Network make it easy to directly support the people who make Nostr better.
5️⃣ Develop New Nostr Apps & Tools
If you're a developer, you can build on Nostr’s open protocol to create new apps, bots, or tools. Nostr is permissionless, meaning anyone can develop for it.
✅ Create new Nostr clients with unique features and user experiences.\ ✅ Build bots or automation tools that improve engagement and usability.\ ✅ Experiment with decentralized identity, authentication, and encryption to make Nostr even stronger.
With no corporate gatekeepers, your projects can help shape the future of decentralized social media.
6️⃣ Promote & Educate Others About Nostr
Adoption grows when more people understand and use Nostr. You can help by spreading awareness and creating educational content.
✅ Write blogs, guides, and tutorials explaining how to use Nostr.\ ✅ Make videos or social media posts introducing new users to the protocol.\ ✅ Host discussions, Twitter Spaces, or workshops to onboard more people.
The more people understand and trust Nostr, the stronger the ecosystem becomes.
7️⃣ Support Open-Source Nostr Projects
Many Nostr tools and clients are built by volunteers, and open-source projects thrive on community support.
✅ Contribute code to existing Nostr projects on GitHub.\ ✅ Report bugs and suggest features to improve Nostr clients.\ ✅ Donate to developers who keep Nostr free and open for everyone.
If you're not a developer, you can still help with testing, translations, and documentation to make projects more accessible.
🚀 Every Contribution Strengthens Nostr
Whether you:
✔️ Post and engage daily\ ✔️ Zap creators and developers\ ✔️ Run or support relays\ ✔️ Build new apps and tools\ ✔️ Educate and onboard new users
Every action helps make Nostr more resilient, decentralized, and unstoppable.
Nostr isn’t just another social network—it’s a movement toward a free and open internet. If you believe in digital freedom, privacy, and decentralization, now is the time to get involved.
-
 @ 9e69e420:d12360c2
2025-02-17 17:12:01
@ 9e69e420:d12360c2
2025-02-17 17:12:01President Trump has intensified immigration enforcement, likening it to a wartime effort. Despite pouring resources into the U.S. Immigration and Customs Enforcement (ICE), arrest numbers are declining and falling short of goals. ICE fell from about 800 daily arrests in late January to fewer than 600 in early February.
Critics argue the administration is merely showcasing efforts with ineffectiveness, while Trump seeks billions more in funding to support his deportation agenda. Increased involvement from various federal agencies is intended to assist ICE, but many lack specific immigration training.
Challenges persist, as fewer immigrants are available for quick deportation due to a decline in illegal crossings. Local sheriffs are also pressured by rising demands to accommodate immigrants, which may strain resources further.
-
 @ 58537364:705b4b85
2025-05-25 16:31:56
@ 58537364:705b4b85
2025-05-25 16:31:56People often only realize the value of something in two situations: First, before they have it. Second, after they’ve lost it.
This is a tragedy that happens to many. People may have good things in their lives, but they don’t see their worth— because they’re always looking outward, focusing on what they don’t have, wishing for something else.
It’s similar to Aesop’s fable about the dog and the piece of meat. We probably remember it from childhood: A dog had a big piece of meat in its mouth. Delighted, it ran to a quiet place where it could enjoy the meat in peace.
At one point, it had to cross a bridge. Looking down into the stream below, it saw its reflection— but mistook it for another dog with an even bigger piece of meat. It wanted that bigger piece badly, so it opened its mouth to snatch it— and the meat in its own mouth fell into the water. The reflection disappeared too.
In the end, it lost both.
So, if we learn to value what we already have, happiness comes easily. It might not be possessions or people— it might simply be our health.
It could be as simple as our breath, the ability to breathe normally, to walk around freely, to see, to hear.
Many people already have these things but don’t recognize their value. They don’t feel lucky. Instead, they focus on what they still lack— no house, no car, no money— and feel miserable.
They ask, “Why is life so hard for me?” Even though they have so many good things already— health, normalcy, freedom of movement— they fail to see it, because their minds are lost in chasing what they don’t yet have, which belongs to the future.
If we turn back and learn to value what we already possess, and stop obsessing over what we don’t, we can find happiness more easily.
This is one of the meanings of “Doing your best in the present.”
…
Doing Your Best in the Present by Phra Paisal Visalo
-
 @ bf47c19e:c3d2573b
2025-05-26 21:26:19
@ bf47c19e:c3d2573b
2025-05-26 21:26:19U ovoj sekciji pratićemo cene raznih dobara i usluga, a pre svega nekretnina, prosečne srpske plate, goriva, deviznih i zlatnih rezervi Srbije u odnosu na Bitkoin. Iz priloženih grafikona može se videti da sve vremenom gubi vrednost, odnosno postaje jeftinije u odnosu na BTC.
Cene nekretnina u Republici Srbiji izražene kroz Bitkoin (kompletni grafikoni)
Visina prosečne zarade u Republici Srbiji, cene goriva, dinarska i devizna štednja stanovništva, devizne i zlatne rezerve Srbije - izraženo kroz Bitkoin (kompletni grafikoni)
Prosečna cena m2 stana u Gradu Beogradu izražena kroz BTC
Prosečna cena m2 stana u Novom Sadu izražena kroz BTC
Prosečna cena m2 stana u Nišu izražena kroz BTC
Prosečna cena m2 stana u Kragujevcu izražena kroz BTC
Prosečna zarada u Republici Srbiji izražena kroz BTC
Cena goriva 'Evro Premium BMB 95' izražena kroz BTC
Cena goriva 'Evro Dizel' izražena kroz BTC
Dinarska štednja stanovništva kod banaka izražena kroz BTC
Devizna štednja stanovništva kod banaka izražena kroz BTC
Devizne rezerve Republike Srbije izražene kroz BTC
Zlatne rezerve Republike Srbije izražene kroz BTC
-
 @ 9223d2fa:b57e3de7
2025-05-25 16:09:51
@ 9223d2fa:b57e3de7
2025-05-25 16:09:512,143 steps
-
 @ 58537364:705b4b85
2025-05-25 15:38:04
@ 58537364:705b4b85
2025-05-25 15:38:04พระอาจารย์ไพศาล วิสาโล วัดป่าสุคะโต แสดงธรรมเย็นวันที่ 28 กันยายน 2565

ที่ประเทศจีนเมื่อสัก 100 - 200 ปีก่อน ชายคนหนึ่งตาบอด แต่ก็สามารถใช้ชีวิตได้ตามปกติ วันหนึ่งก็เดินไปเยี่ยมเพื่อน ซึ่งอยู่ในเมืองเดียวกัน แต่ก็เดินไกลสักหน่อย แล้วชายตาบอดคนนี้ก็เดินได้โดยที่ไม่ต้องใช้ไม้เท้า ถึงบ้านเพื่อนก็สนทนากับเพื่อนหลายเรื่องหลายราว คุยกันถูกคอ จนกระทั่งค่ำ ก็ได้เวลาที่ชายตาบอดจะกลับบ้าน แต่ก่อนที่แกจะเดินออกจากบ้าน เพื่อนก็ยื่นโคมให้ โคมนี่เป็นคนที่จุดไฟให้แสงสว่างในเวลากลางคืน
ชายตาบอดก็บอกว่าฉันไม่ต้องใช้โคมหรอก เดินได้โดยที่ไม่เห็นอะไร ไม่ต้องใช้แสงสว่างก็เดินได้ ทางเส้นนี้ฉันก็คุ้นแล้ว เพื่อนก็บอกว่าที่ให้โคมนี่ ก็เพื่อเวลาคุณเดินกลับบ้านตามตรอกซอกซอย มันจะได้ให้แสงสว่าง คนที่เขาเดินสวนคุณมา เขาเห็นทาง เขาก็จะได้ไม่เดินชนคุณไงล่ะ เหตุผลนี้ก็ทำให้ชายตาบอดถือโคมกลับบ้าน ทั้งๆ ที่ตัวเองไม่จำเป็นต้องใช้โคมนั้นเลย
ระหว่างที่เดินกลับบ้านก็มีคนหลายคนเดินสวน เพราะมันเป็นตรอกซอกซอยที่มีคนเดินผ่านไปผ่านมาอยู่ แต่ว่าพอเดินมาพักหนึ่ง ปรากฏว่ามีผู้ชายคนหนึ่งเดินชนชายตาบอดอย่างแรงเลย จนล้มเลย ชายตาบอดก็โกรธมาก ก็พูดขึ้นมาว่าแกตาบอดหรือไง แกไม่เห็นหรือโคมที่ฉันถือนี่ ชายคนที่เดินชนชายตาบอดก็บอกว่าขอโทษครับ ขอโทษจริงๆ แต่โคมที่พี่จุดนี่มันดับไปนานแล้วนะ เรื่องก็จบเท่านี้นะ ฟังแล้วเราได้แง่คิดอะไรไหม
เรื่องนี้อาจจะเป็นนิทานนะ แต่มันไม่ใช่นิทานประเภทว่าสอน บอกเราในตอนท้ายว่านิทานเรื่องนี้สอนอะไร แต่ว่ามันจบลงโดยให้เราคิดเอง ฟังเรื่องนี้แล้วเราได้แง่คิดอะไร
แง่คิดอย่างหนึ่งก็คือว่าในการดำเนินชีวิตของคนเรา เราควรจะคิดถึงคนอื่นด้วย ของบางอย่างเราไม่จำเป็น แต่ว่ามันมีประโยชน์กับคนอื่น ถ้าเรานึกถึงคนอื่น มันก็ไม่ใช่ประโยชน์กับคนอื่นอย่างเดียว มันเป็นประโยชน์กับเราด้วย อย่างชายตาบอด เขาไม่จำเป็นต้องใช้โคมเลย ในการเดินกลับบ้านยามค่ำคืน แต่เพื่อนคะยั้นคะยอให้ถือโคมเพื่ออะไร ก็เพื่อประโยชน์ของคนอื่นที่เขาตาดี แล้วเขาต้องใช้แสงสว่างในการเดินสัญจร
การที่ชายตาบอดถือโคม ไม่ได้เพื่อประโยชน์ของตัวเอง แต่เพื่อประโยชน์ของคนอื่น แต่สุดท้ายมันก็เป็นประโยชน์กับตัวเอง เพราะถ้าหากว่าคนที่เขาเดินสวนมา เขาเห็นชายตาบอดถือโคม เขาก็ไม่เดินชน ฉะนั้นทีแรกชายตาบอดก็เดินได้สะดวกสบาย ไม่มีใครชน ก็เพราะว่าคนอื่นเขาเห็นแสงสว่างจากโคมนั้น
อันนี้เขาสอนว่าคนเราควรจะนึกถึงผู้อื่น ของบางอย่างแม้เราไม่จำเป็น แต่ว่ามันเป็นประโยชน์กับผู้อื่นก็ควรทำ หรือบางอย่างอาจจะไม่สะดวกกับเรา แต่ว่ามันช่วยคนอื่นได้ อย่างเช่นการถือโคม มันคงไม่สะดวกสบายเท่ากับเดินตัวเปล่า แต่ว่าเมื่อเดินถือโคมแล้ว มันก็เป็นประโยชน์กับคนที่เดินสวนมาด้วย แต่สุดท้ายมันก็กลับมาเป็นประโยชน์กับชายตาบอดนั่นเอง อย่างที่พูดไปแล้ว ไม่มีใครมาเดินชน
ในชีวิตของคนเรา เราควรจะคิดถึงคนอื่น ฉะนั้นการที่สังคมหรือบ้านเมืองมันน่าอยู่ ก็เพราะผู้คนไม่ได้คิดถึงแต่ตัวเองอย่างเดียว การกระทำบางอย่าง เราทำเพื่อประโยชน์ของส่วนรวม เพื่อผู้อื่น ยกตัวอย่างง่ายๆ เวลาเรากินอะไร มันมีขยะอยู่ในมือ จะเป็นถุงพลาสติก จะเป็นนมกล่อง หรือจะเป็นขวด ขวดน้ำที่กลายเป็นขยะเรียบร้อยแล้ว ทำไมเราควรจะถือขยะนั้นไว้กับตัว จนกว่าจะเห็นถังขยะจึงหย่อนลงถังขยะ
ที่จริงถ้าเรานึกถึงแต่ตัวเอง เราก็แค่โยนมันทิ้งขยะนั้นข้างทาง สบายดีนะ หลายคนก็ทำอย่างนั้น คนเราถ้าคิดถึงแต่ตัวเอง เราไม่เก็บมันไว้กับตัว แล้วก็รอจนกว่าจะเดินเห็นถังขยะ แต่คนจำนวนมากเขาก็เก็บขยะเอาไว้ เพื่อที่จะไปทิ้งลงในถังขยะ
อันนี้เพราะอะไร เพราะนึกถึงผู้อื่น นึกถึงคนที่เก็บขยะบ้าง หรือนึกถึงสังคมส่วนรวม ว่าถ้าเราทิ้งขยะไม่เป็นที่ มันก็จะเลอะเทอะ ไม่น่าดู บางคนก็คิดถึงพนักงานเก็บขยะ หรือคิดถึงพนักงานทำความสะอาด ก็เลยช่วยเขาด้วยการทิ้งขยะเป็นที่ ทั้งที่ถ้าทิ้งข้างทาง กินเสร็จ ดื่มน้ำเสร็จ ดูดนมกล่องเสร็จ ทิ้งไปเลยนี่มันสบายกว่า แต่เป็นเพราะเราคิดถึงคนอื่น เราจึงเอาไปทิ้งเป็นที่
หรือการปิดไฟ บางทีเราก็เห็นไฟเปิดอยู่ที่ห้องน้ำ หรือที่ห้องที่โล่ง เราก็อุตส่าห์เดินไป แทนที่เราจะกลับบ้านเลย เราก็เดินไปที่ห้องน้ำเพื่อที่จะปิดสวิตช์ไฟ เรายอมเสียเวลาเพื่ออะไร ก็เพื่อส่วนรวม หรืออาจจะเป็นเพราะว่าเราอยากจะช่วยพนักงานที่เขาดูแลสถานที่นั้น ไม่ต้องเหนื่อยกับการวิ่งการเดินตามปิดไฟ ที่วัดเราเป็นระเบียบ ก็เพราะผู้คนจำนวนมากคิดถึงผู้อื่นด้วย ไม่ได้คิดถึงแต่ตัวเอง และสุดท้ายมันก็เป็นประโยชน์กับตัวเรา เพราะว่าพอสถานที่มันสะอาดหมดจด มันก็สบายหูสบายตา น่าอยู่
แต่ว่านิทานเรื่องนี้เขาสอนมากกว่านั้น ในการดำเนินชีวิตประจำวัน เราควรจะคิดถึงผู้อื่น มองไปที่ประโยชน์ของคนอื่นก่อนตัวเอง แต่เวลามีปัญหาขึ้นมา ก่อนที่จะไปโทษคนอื่น ต้องกลับมามองที่ตัวเองก่อน ไม่เหมือนกันนะ ยามปกติเรามองไปที่คนอื่นก่อน นึกถึงประโยชน์ของคนอื่นก่อน ประโยชน์ของตัวเองเอาไว้ทีหลัง แต่ว่าเวลามีปัญหา เราควรมองที่ตัวเองก่อนที่จะไปโทษคนอื่น
อย่างชายตาบอดนี่ พอมีคนมาชน แกก็ว่าชายคนนั้นเลยทีเดียว ว่าตาบอดหรือไง มาชนเขา แต่เขาไม่รู้ว่าที่เขาถูกชน เป็นเพราะว่าโคมของเขามันดับไปแล้ว ชายคนนั้นก็เลยมองไม่เห็น แต่ชายตาบอดจะรู้ได้อย่างไร ว่าโคมของตัวเองนี่ดับไปแล้ว อันนี้เหมือนกับสอนเป็นนัยว่าคนที่โทษคนอื่น แทนที่จะมองมาที่ตัวเอง จะว่าไปก็เหมือนกับคนตาบอด คือมองไม่เห็นความบกพร่อง ความผิดพลาดของตัวเอง อันนี้ก็รวมถึงคนตาดีด้วยนะ คนตาดีถ้าเกิดปัญหาขึ้นมาแล้ว ไปโทษคนอื่น แต่มองไม่เห็นความบกพร่อง ความผิดพลาดของตัวเอง ก็ไม่ต่างจากคนตาบอดเหมือนกัน
อันนี้ก็เป็นข้อคิดที่ดีมากเลย ในยามปกติเราควรนึกถึงผู้อื่น มองไปที่คนอื่นก่อน แต่เวลามีปัญหาควรจะกลับมามองที่ตัวเอง ก่อนที่จะไปโทษคนอื่น อันนี้จะเรียกว่าเป็นวิสัยของนักปฏิบัติธรรมก็ได้ จะเรียกว่าเป็นวิสัยของผู้ใฝ่ธรรม ซึ่งต่างจากวิสัยของชาวโลกทั่วๆ ไป ชาวโลกทั่วไปเขามองตัวเองก่อน เขามองถึงประโยชน์ตัวเองก่อน คิดถึงตัวเองก่อน ส่วนคนอื่น ประโยชน์ของคนอื่นเอาไว้ทีหลัง แต่เวลามีปัญหาขึ้นมา ก็โทษคนอื่นก่อนเลย แทนที่จะกลับมามองที่ตัวเอง
บ่อยครั้งเวลางานมีปัญหา เราจะเห็นคนก็จะไปโทษคนโน้นคนนี้ ว่าเป็นเหตุทำให้งานมีปัญหา ทำให้งานตัวเองมีปัญหา เจ้านายไม่ดี เพื่อนร่วมงานไม่ได้เรื่อง บางทีก็โทษดินฟ้าอากาศ แต่ว่าสิ่งที่ไม่ได้มองคือความผิดพลาดของตัวเอง เวลานัดเพื่อน เพื่อนไม่มาตามนัดตามเวลา ก็โกรธเพื่อน พอเจอเพื่อนก็ไปด่าเพื่อนเลย ว่าทำไมนัด 4 โมงเย็น ทำไมไม่มา อุตส่าห์รอ
เพื่อนบอกอ้าวจะไปรู้เหรอ นึกว่านัด 4 โมงเช้า ผมก็อุตส่าห์ไปรอตั้งแต่ 4 โมงเช้า คือ 10 โมง ปรากฏว่าคนนัดบอกเวลาไม่ละเอียด แทนที่จะบอก 4 โมงเย็น ก็ไปพูดว่า 4 โมง เพื่อนก็เลยนึกว่า 4 โมงเช้า เป็นความผิดพลาดของคนนัดแท้ๆ แต่ว่าก็ไปด่าเพื่อนเสียแล้ว ตัวเองพูดไม่ละเอียด ก็ไปโทษเพื่อน ว่าเพื่อนไม่รับผิดชอบ เพื่อนไม่เอาใจใส่
อันนี้เรียกว่าไปโทษคนอื่นก่อนที่จะมามองที่ตัวเอง ถ้าจะให้ดีก็ควรจะถามเขาก่อนว่าทำไมถึงไม่มาตามนัด พอรู้คำอธิบายของเพื่อน ก็อาจจะพบว่าเป็นเพราะเราผิดเองนะ เราพูดไม่รัดกุมเพียงพอ ที่จริงมันไม่ใช่เฉพาะเวลามีความผิดพลาด หรือเวลามีปัญหาในงานการ เวลามีความทุกข์ก็เหมือนกัน เวลามีความทุกข์ก่อนที่จะไปโทษใคร ต้องกลับมามองที่ตัวเองก่อน แต่คนส่วนใหญ่เวลามีความทุกข์ ไปโทษข้างนอก ไปโทษเสียงดังจากข้างนอก ไปโทษการกระทำของคนนั้นคนนี้ แต่ลืมหรือไม่ได้กลับมามองที่ตัวเอง ว่าเป็นที่เราหรือเปล่า
เวลามีความทุกข์ใจ สาเหตุหลักๆ มันล้วนแล้วแต่อยู่ที่ตัวเองทั้งนั้นแหละ ไม่ได้อยู่ที่คนอื่น ทุกข์กายอาจจะเป็นเพราะของแหลมมาแทง อาจจะเป็นเพราะเชื้อโรค เพราะอาหารเป็นพิษ หรือเพราะมีคนมาทำร้าย แต่ถ้าทุกข์ใจแล้วนี่ มันน่าจะเกิดจากตัวเอง หรือใจของตัวเองเป็นหลักเลยทีเดียว
เมื่อสัก 40 กว่าปีก่อน หลวงพ่อชาท่านได้รับนิมนต์ให้มาแสดงธรรมที่ประเทศอังกฤษ ตอนนั้นท่านก็มากับลูกศิษย์ที่เป็นพระฝรั่ง เช่นหลวงพ่อสุเมโธ ซึ่งตอนนั้นยังไม่ได้สร้างวัดอมราวดีที่อังกฤษ เจ้าภาพก็ให้หลวงพ่อชากับลูกศิษย์พักที่วิหารกลางกรุงลอนดอน ย่านนั้นมีสถานบันเทิง เช่น ผับ บาร์ กลางคืนก็จะมีเสียงดนตรี
สมัยนั้นดิสโก้ก็เริ่มเป็นที่นิยมแล้ว เพราะฉะนั้นเสียงดังก็จะกระหึ่มเลยตอนกลางคืน มาถึงวิหารแฮมสเตทที่หลวงพ่อชาและลูกศิษย์พัก ซึ่งก็พอดีเป็นช่วงที่ท่านพาคนนั่งสมาธิ พระและโยมหลายคนนั่งสมาธิไม่เป็นสุขเลย เพราะเสียงดนตรีมันดัง
แต่หลวงพ่อชาท่านนั่งสมาธิอย่างสงบ เหมือนกับไม่ได้ยินอะไรเลย จนกระทั่งนั่งสมาธิเสร็จ ก็มีโยมซึ่งเป็นฝรั่ง เป็นเจ้าภาพ ก็มาหาท่านแล้วก็บอกขอโทษ ที่เสียดนตรีรบกวนการนั่งสมาธิ หลวงพ่อชาท่านฟังแล้วก็ยิ้ม แล้วท่านก็พูดว่าโยมอย่าไปคิดว่าเสียงดนตรีรบกวนเรา ที่จริงเราต่างหากที่ไปรบกวนเสียงดนตรี
บางคนฟังแล้วก็งงนะ แต่ที่จริงที่ท่านพูดนี่มันเป็นสัจธรรมเลยนะ ที่คนมีความทุกข์ หงุดหงิด เมื่อเสียงมากระทบหู มันไม่ใช่เพราะเสียง แต่เป็นเพราะใจมันไปทะเลาะกับเสียงนั้น ใจมันไปต่อสู้ ไปทะเลาะเบาะแว้งกับเสียงนั้น มันไปผลักไสเสียงนั้น ถ้าเพียงแต่ยอมรับเสียงนั้น มันก็ไม่หงุดหงิด แต่พอใจมันทะเลาะกับเสียง เพราะว่ามีความรู้สึกเป็นลบต่อเสียงนั้น ว่าเป็นเสียงดัง เสียงรบกวน พอใจรู้สึกเป็นลบ มันหงุดหงิดขึ้นมาเลย ความหงุดหงิดจนนั่งสมาธิไม่เป็นสุข เป็นเพราะใจของคนฟัง ที่วางใจไม่ถูกต้องต่อเสียง ถ้าหากว่าเพียงแต่รู้สึกเป็นกลางๆ มันก็ไม่ทุกข์
มีนักปฏิบัติธรรมคนหนึ่ง แกก็มาปฏิบัติอยู่ที่สำนักหรือวัดแห่งหนึ่ง ก็ค้างคืนอยู่ประมาณ 2-3 คืน คืนแรกเลย พักเสร็จตื่นเช้าขึ้นมา เจ้าอาวาสก็ถามว่า เป็นยังไง หลับดีไหม ชายคนนั้นก็บอกว่าหลับไม่ค่อยดี โดยเฉพาะช่วงแรกๆ เพราะว่าเสียงห่านมันดัง
เสียงห่านมันดัง ตอนกลางคืนนอนไม่ค่อยหลับเลยช่วงแรก แต่ว่านึกขึ้นมาได้ว่าตัวเองพกโทรศัพท์มือถือมา แล้วในโทรศัพท์มือถือก็มีการอัดเทปคำบรรยายธรรมะของครูบาอาจารย์หลายท่าน ก็เลยเอาหูฟังใส่ไว้ในหู แล้วก็ฟัง เปิดเทปธรรมะ เปิดคำบรรยายของครูบาอาจารย์ จนกระทั่งหลับได้ กระทั่งเช้าก็เป็นอันว่าได้พัก ได้หลับดีหน่อยช่วงครึ่งหลัง
สิ่งที่น่าสนใจคือว่า ระหว่างเสียงห่านกับเสียงบรรยาย อะไรดังกว่ากัน ชายคนนั้นบอกว่าหลับไม่ได้ เพราะว่าเสียงห่านมันดัง แต่เสียงบรรยายที่ฟังมันไม่ดังหรือ ที่จริงมันดังกว่าเสียงห่าน เพราะว่าเอาหูฟังใส่เข้าไปในรูหู อย่างไรมันดังกว่าเสียงห่านอยู่แล้วล่ะ แต่ทำไมหลับ ก็เพราะใจมันยอมรับเสียงบรรยายธรรมะ หรือว่ารู้สึกดีกับเสียงนั้น ขณะที่เสียงห่านนี่ ใจมองว่าเป็นเสียงรบกวน การที่ใจไปตีค่าว่าเสียงห่านเป็นเสียงรบกวน ก็ทำให้เกิดอาการต่อสู้ผลักไสกับเสียงนั้น
เหมือนอย่างที่หลวงพ่อชาท่านว่าไปทะเลาะกับเสียง ส่วนเสียงบรรยายธรรมะที่ฟังทางโทรศัพท์มือถือ ใจมันยอมรับ ใจมันรู้สึกเป็นบวก เลยไม่รู้สึกว่าดัง ทั้งที่ถ้าพูดถึงเดซิเบลแล้ว มันดังกว่าเสียงห่านอยู่แล้วแต่ก็เป็นอันหลับได้ ฉะนั้นที่หลับไม่ได้ ไม่ใช่เพราะเสียงดัง ไม่ใช่เพราะเสียงห่าน แต่เพราะใจมันไปทะเลาะกับเสียงห่าน ในขณะที่เสียงบรรยายใจไม่ได้ทะเลาะ ใจไปเคลิ้มคล้อยกับเสียงบรรยายธรรมเลยหลับ
นี่เป็นตัวอย่างง่ายๆ ในชีวิตของคนเรา เวลามีความทุกข์ ทุกข์ใจ เรามักโทษข้างนอก โทษเสียงดนตรี โทษเสียงห่าน โทษคนนั้นคนนี้ แต่นั่นเป็นเพราะเราไม่ได้กลับมาดูใจของเรา ไม่ได้กลับมาสังเกตปฎิกริยาของใจเรา ฉะนั้นถ้าเรากลับมาสังเกต ก็จะพบว่ามันเป็นเพราะใจของเราต่างหาก ที่เป็นตัวการทำให้เกิดทุกข์
ฉะนั้นถ้าเกิดว่าเรามีทุกข์ หรือมีปัญหาขึ้นมาในใจ แล้วเราไปมองออกนอกตัว ไม่กลับมามองที่ตัว ก็ไม่ต่างจากชายตาบอด ที่ไปต่อว่าคนที่มาชนตัวเอง ทั้งที่โคมที่ตัวเองถือ ไฟมันดับไปนานแล้ว แต่มองไม่เห็น วิถีธรรมกับวิถีโลกมันต่างกัน วิถีโลก มีปัญหาอะไรก็โทษคนอื่น แต่เวลาสบายก็คิดถึงแต่ตัวเอง ส่วนวิถีธรรม เวลาสบายๆ เวลาปกติก็นึกถึงคนอื่น แต่เวลามีปัญหาก็กลับมองที่ตัวเองก่อน
แล้วที่จริงถ้าเราดู มันสะท้อนให้เห็นว่า วิถีโลกเขาเน้นในเรื่องการเปลี่ยนแปลง จัดการกับภายนอก แต่ว่าวิถีธรรมหรือวิถีของผู้ใฝ่ธรรม จะเน้นที่การเปลี่ยนแปลงที่ตัวเอง โดยเฉพาะการปรับเปลี่ยนใจของตัว เวลามีความทุกข์ก็ลองปรับเปลี่ยนใจ

เหมือนมีผู้ชายคนหนึ่งที่เขานั่งสมาธิทุกเช้าเป็นประจำ แล้วเขาก็นั่งได้ดีด้วย แต่วันหนึ่งปรากฏว่าพอนั่งไปได้สักครู่หนึ่ง ก็มีเสียงค้อนดัง ทีแรกก็เสียงค้อน ตอนหลังก็เสียงเลื่อยยนต์ เพราะมีการก่อสร้างใกล้ๆ ตอนที่เสียงค้อน เสียงเลื่อยยนต์มากระทบหู ใจนี่ก็กระเพื่อมเลย แต่เขามีสติเห็น สติรู้ทัน พอมีสติรู้ทัน ใจก็สงบ แต่พอเผลอ ใจก็กระเพื่อม ทุกครั้งที่เสียงเลื่อยยนต์ดังกระทบหู แล้วมันก็สงบลงพอมีสติรู้ทัน เป็นอย่างนี้พักหนึ่ง
เขาก็เลยลองไปพิจารณาที่เสียงเลื่อยยนต์ พอพิจารณาไปก็สังเกตว่าบางครั้งมันก็กระชากกระชั้น บางครั้งมันก็ลากยาว บางครั้งเสียงสูง บางครั้งเสียงต่ำ บางครั้งเสียงดัง บางครั้งเสียงเบา ดูๆไปแล้วมันเหมือนกับเสียงเพลงเลยนะ เพลงประเภท heavy metal พอทันทีที่มองว่ามันเป็นเสียงเพลง ใจก็สงบเลย สงบประเภทที่ว่าเพลินเลย
ที่จริงเพลินก็ไม่ดี แต่เขาก็อดฉุกคิดไม่ได้ เอ๊ะ เมื่อกี้ใจยังกระเพื่อมขึ้นกระเพื่อมลง แถมมีความหงุดหงิดด้วย ตอนนี้ทำไมใจมันสงบ มีบางช่วงเสียงเลื่อยยนต์มันหายไป เขาอยากให้เสียงมันดังกลับมาใหม่ เขาก็เลยแปลกใจ ทีแรกเราอยากให้เสียงมันดับไปหายไป แต่ทำไมตอนนี้อยากให้เสียงมันดังใหม่ เสียงมันก็ยังดังเหมือนเดิม แต่ทำไมความรู้สึกเปลี่ยนไป
ที่ความรู้สึกเปลี่ยนไปเพราะอะไร เพราะว่าไม่ได้มองว่ามันเป็นเสียงดังอีกต่อไป แต่มองว่ามันเป็นเสียงเพลง พอมองว่าเป็นเสียงเพลง ความรู้สึกมันเป็นความรู้สึกในทางบวก ใจก็สงบเลย อันนี้มันก็ชี้ให้เห็นว่าความสงบมันอยู่ที่ใจ มากกว่าอยู่ที่สิ่งภายนอก และที่หงุดหงิด ที่ไม่สงบ มันไม่ใช่เพราะสิ่งภายนอก แต่เป็นเพราะใจ ใจรู้สึกลบกับเสียง มันก็กระเพื่อม มันก็หงุดหงิด ไม่สงบ ไม่เป็นสุข แต่พอใจรู้สึกเป็นบวก ความรู้สึกก็เปลี่ยนเป็นตรงกันข้าม
ฉะนั้นแทนที่จะไปตะโกนโวกเวกว่าให้หยุดส่งเสียง ให้เลิกตอกตะปู ให้เลิกใช้เลื่อยยนต์ มันจะดีกว่าหรือเปล่า ถ้ากลับมาดูที่ใจของเรา กลับมาสังเกตที่ใจของเรา หรือกลับมาปรับใจของเรา ใจของเรานี่อาจจะเป็นปัญหา
อันนี้คล้ายๆ กับเมื่อ 2-3 วันก่อน มีพระรูปหนึ่งเล่าให้ฟัง ได้ยินเสียงตอนเช้าๆ ที่วัด ตอนสายๆ วันกรรมกร มันมีเสียงเครื่องยนต์ดัง ตอนนั้นก็คิดว่าเป็นเสียงมอเตอร์ไซค์ ทันทีที่คิดว่าเป็นเสียงมอเตอร์ไซค์ ไม่พอใจขึ้นมาทันทีเลย มันมาขี่มอเตอร์ไซค์อะไรกันตรงนี้ ในวัด
แต่สักประเดี๋ยวเดียวฉุกขึ้นมาว่าเอ๊ะ มันอาจจะไม่ใช่เสียงมอเตอร์ไซค์ก็ได้ อาจจะเป็นเสียงเลื่อย เลื่อยที่เขากำลังตัดไม้ที่โค่น เพราะว่าก่อนหน้านั้นมีไม้โค่น ทันทีที่นึกว่าเป็นเสียงเลื่อย ที่ใช้ตัดไม้ที่ล้มลง ใจมันสงบเลย กลับอนุโมทนาด้วย เขามาช่วยกันทำงาน เสียงก็เสียงเดิม แต่ทำไมทีแรกหงุดหงิด เพราะไปคิดว่าเสียงมอเตอร์ไซค์ และคิดต่อไปว่ามันมาขี่อะไรแถวนี้ ในวัด แต่พอมองว่าเป็นเสียงเลื่อยที่ใช้เลื่อยไม้ที่ล้ม ความรู้สึกมันเปลี่ยนไป เพราะเกิดความรู้สึกว่าเขากำลังทำหน้าที่ของเขา
ฉะนั้นสุขหรือทุกข์อยู่ที่ใจแท้ๆ เลย หงุดหงิดหรือว่าสงบ อยู่ที่ใจ ไม่ใช่อยู่ที่เสียง อยู่ที่ว่าเราจะมองมันอย่างไร ฉะนั้นถ้าเราเข้าใจตรงนี้ สังเกตใจของเรา เราจะพบว่าจะไปแก้ทุกข์ก็ต้องแก้ที่ใจนั่นแหละ ไม่ต้องไปแก้ที่คนอื่น เป็นเพราะใจเราวางไว้ผิด มันจึงทุกข์ มันจึงเกิดความหงุดหงิด เกิดความรำคาญ แต่พอเราปรับใจ เปลี่ยนมุมมอง ความรู้สึกก็เปลี่ยนไป
zen sukato บันทึกเสียง Nun & oi ถอดเสียง nok edit
-
 @ fd208ee8:0fd927c1
2025-02-15 07:02:08
@ fd208ee8:0fd927c1
2025-02-15 07:02:08E-cash are coupons or tokens for Bitcoin, or Bitcoin debt notes that the mint issues. The e-cash states, essentially, "IoU 2900 sats".
They're redeemable for Bitcoin on Lightning (hard money), and therefore can be used as cash (softer money), so long as the mint has a good reputation. That means that they're less fungible than Lightning because the e-cash from one mint can be more or less valuable than the e-cash from another. If a mint is buggy, offline, or disappears, then the e-cash is unreedemable.
It also means that e-cash is more anonymous than Lightning, and that the sender and receiver's wallets don't need to be online, to transact. Nutzaps now add the possibility of parking transactions one level farther out, on a relay. The same relays that cannot keep npub profiles and follow lists consistent will now do monetary transactions.
What we then have is * a transaction on a relay that triggers * a transaction on a mint that triggers * a transaction on Lightning that triggers * a transaction on Bitcoin.
Which means that every relay that stores the nuts is part of a wildcat banking system. Which is fine, but relay operators should consider whether they wish to carry the associated risks and liabilities. They should also be aware that they should implement the appropriate features in their relay, such as expiration tags (nuts rot after 2 weeks), and to make sure that only expired nuts are deleted.
There will be plenty of specialized relays for this, so don't feel pressured to join in, and research the topic carefully, for yourself.
https://github.com/nostr-protocol/nips/blob/master/60.md
-
 @ 2b998b04:86727e47
2025-05-26 21:05:47
@ 2b998b04:86727e47
2025-05-26 21:05:47Today I pause — not to celebrate, but to remember.\ Memorial Day is a reminder that freedom always comes at a cost. Not theoretical. Not digital. Real. Blood-bought. Passed down.
I didn’t earn the liberties I have. Someone else paid for them.\ The least I can do is steward them well — in how I live, build, and speak.
Tomorrow, I head to Bitcoin 2025.\ I go not just as a Bitcoiner, but as someone who believes Bitcoin, when rightly understood, calls us back to truth, cost, and accountability.\ Not magic internet money. Not another tech trend.\ But a reckoning.
So I walk into this week with both gratitude and resolve:
-
Grateful for those who gave their lives.
-
Grateful for the freedom to write, build, and think out loud.
-
Resolved to use that freedom wisely — and to build systems that don't require bloodshed to sustain them.
Let’s build what lasts.\ Let’s remember what was paid.\ Let’s walk into Bitcoin 2025 with clear eyes and full hearts.
-
-
 @ 2b998b04:86727e47
2025-05-26 20:56:42
@ 2b998b04:86727e47
2025-05-26 20:56:42Why Trading Matters (And Why It’s Not a Zero-Sum Game)
There’s a common belief — even in some Bitcoin circles — that short-term trading is just gambling. That it’s a zero-sum game where one trader’s win is another’s loss.
I get it. The noise is real. So is the wreckage from over-leveraged bets and mindless speculation.
But that’s not the whole story.
Recently, someone I worked with in 2023 and 2024 — a former mortgage broker — invited me to join an “investment club” that sends buy/sell signals through WhatsApp.\ Just follow the messages. Don’t think. Don’t learn. Just click and hope.
That’s not trading.\ That’s waiting on an oracle and outsourcing your judgment. It’s faith in hype, not process. It’s anti-skill.
Another friend told me my approach — aiming for consistent, small intraday gains — sounded boring. But here’s what I told him:
If I trade a $100 stock ten times in a day for a $1–2 gain each time, I’ve made the same as someone waiting around for that one 10% spike.\ But I’ve done it with discipline, risk control, and real engagement. That’s not boring. That’s working.
These days, I only trade equities. No crypto. No forex.
Why? Because equities are productive assets tied to real businesses in a real economy.\ They aren’t my end goal — Bitcoin is.\ But equities offer a stable, regulated environment to extract short-term gains without feeding the casino culture of leveraged altcoins or hypervolatile FX pairs.
And forex? You're just trading one melting ice cube for another — flipping between fiat currencies that are backed by nothing but promises and policies.\ It's like playing musical chairs with pieces of paper while the music gets faster.\ I’ve done it. I understand it. But it no longer feels congruent with my Bitcoin ethos.
It’s not about purity. It’s about alignment.\ If I’m going to trade, I want the process to reflect the same principles that drew me to Bitcoin: transparency, discipline, and long-term thinking.
Real trading is:
-
Dynamic, not zero-sum.\ While some instruments are win/lose, markets as a whole reward liquidity, attention, and adaptability. Traders contribute to price discovery.
-
A funding mechanism for conviction.\ I don’t trade just to make money — I trade to build. My equity gains fund my Bitcoin stacking, my open-source work, my writing, my peace of mind.
-
A craft, not a shortcut.\ The edge is earned. Over time. In silence. With scars.
I’m not here to follow someone’s signals.\ And I’m not chasing that one moonshot.
This is daily work.\ This is Proof of Work.
Postscript:\ This week? No red days. A green week — around $300.\ Not a huge number. And that’s okay.\ Because I wasn’t just trading.
I was writing. Building. Launching tools. Finishing a 5-part series.\ Some weeks, the return isn’t measured in dollars. It’s measured in direction.
Small trades. Strong conviction. Deep alignment.
That’s Proof of Work, too.
-
-
 @ 87fedb9f:0da83419
2025-05-26 19:57:22
@ 87fedb9f:0da83419
2025-05-26 19:57:22https://www.thrivingnow.center/t/1487/5
We covered…
1. Differentiation: Claiming Our Energetic Space
Differentiation isn’t just about closeness or distance—it’s about clearly knowing where we end and others begin. We can say, “They’re tired and grumpy right now,” without giving up our cheerful mood from a peaceful morning meditation. We can adapt without losing ourselves, choosing consciously rather than reacting habitually.
2. Energetic Boundaries: Maintaining Our Own Weather
Many of us with heightened empathy tend to embody another person’s emotions, making their grumpiness our own. Practicing differentiation helps us notice their state without internalizing it, allowing us to maintain our own emotional clarity and calm, even when someone else brings stormy energy into the room.
3. Growing Emotional Muscles Through Discomfort
Differentiation is challenging because it involves tolerating discomfort. For example, preparing a meal lovingly and then watching someone else be disappointed requires emotional resilience. Using EFT tapping, we actively address these uncomfortable moments, building inner strength and clarity to stay true to ourselves even under pressure.
4. Self-Validation: Anchoring Our Integrity
Instead of relying on external validation, we ask ourselves: “Did I act with integrity?” If we’ve lovingly prepared a meal or helped in a situation, we can acknowledge our effort regardless of others’ reactions. By validating ourselves internally, we nurture our sense of self-worth and emotional freedom.
5. Allowing Others Their Own Discomfort
We often feel compelled to alleviate others’ discomfort immediately—yet it’s not always helpful. For instance, when someone is hungover or grumpy, we don’t need to energetically jump in to fix their state. Allowing people to experience their discomfort without interference respects their personal growth and conserves our emotional resources.
6. From Survival Obligations to Conscious Responsiveness
As children, enmeshment—absorbing others’ emotional states—was crucial for survival. As adults, we can shift to a posture of response-ability, being willing and able to respond without obligation. Recognizing we no longer need survival reactions for non-life-threatening situations helps us thrive rather than merely survive emotionally.
7. Honoring the Essential Struggle
Just like a butterfly must struggle out of its chrysalis to survive, allowing someone to face their own challenges supports genuine growth. Even if our heart urges us to intervene, differentiation guides us to remain compassionately present without interfering with their developmental process.
8. Turning Down the Empathy Volume
Many of us developed heightened empathy to monitor emotional threats in childhood. We can now gently turn down this sensitivity, trusting that we’ll notice genuine needs without overreacting to every emotional ripple around us. We use EFT tapping and mindful intentions to recalibrate this empathic awareness.
9. Discernment Check-In: “How Much Is Mine?”
We practice asking ourselves: “How much of this discomfort belongs to me, and how much is theirs?” If we’re triggered by someone’s frustration or disappointment, checking in helps us clarify our own feelings from theirs. For example, recognizing that a child’s intense disappointment resonates with our own unresolved feelings helps us respond more skillfully.
10. Permission to Pause and Choose
When faced with emotional demands—especially from family or intense group dynamics—we give ourselves permission to pause and reflect. We ask, “Is this really my circus, my monkey?” and decide what genuinely feels right. For instance, deciding whether to answer a distressed late-night call from a family member becomes a conscious choice rather than an automatic obligation.
11. Authentic Connections in the “We Space”
Differentiation doesn’t mean isolation—it creates a “we space” where authentic relationships thrive. Being differentiated means we are fully ourselves within relationships, clearly communicating our needs and limits, and respecting those of others. This mutual clarity fosters deeper, healthier connections built on emotional freedom and genuine understanding.
-
 @ 9e69e420:d12360c2
2025-02-14 18:07:10
@ 9e69e420:d12360c2
2025-02-14 18:07:10Vice President J.D. Vance addressed the Munich Security Conference, criticizing European leaders for undermining free speech and traditional values. He claimed that the biggest threat to Europe is not from external enemies but from internal challenges. Vance condemned the arrest of a British man for praying near an abortion clinic and accused European politicians of censorship.
He urged leaders to combat illegal immigration and questioned their democratic practices. “There is a new sheriff in town,” he said, referring to President Trump. Vance's remarks were unexpected, as many anticipated discussions on security or Ukraine. His speech emphasized the need for Europe to share the defense burden to ensure stability and security.
-
 @ cae03c48:2a7d6671
2025-05-25 15:00:49
@ cae03c48:2a7d6671
2025-05-25 15:00:49Bitcoin Magazine

Nigel Farage To Speak At Bitcoin 2025 ConferenceWe are pleased to announce that Nigel Farage will join the speaker lineup at the Bitcoin Conference 2025 in Las Vegas. A defining figure in modern European politics, Farage led the Brexit movement that took the United Kingdom out of the EU, reshaping global conversations around national sovereignty. He is the founder and current leader of Reform UK, a rising political force now polling competitively, positioning him as a serious contender for to be the next UK Prime Minister.
A former Member of the European Parliament for over 20 years, Farage built his reputation challenging supranational institutions and unelected power—values that resonate deeply with the Bitcoin community. He also hosts GB News, where he critiques monetary policy, CBDCs, and digital surveillance. An outspoken advocate for financial sovereignty and free speech, Farage previously appeared at Bitcoin Amsterdam 2023 in a conversation with Peter McCormack. In 2025, he returns for a fireside with Bitcoin Magazine’s Frank Corva, whose sharp political interviews are helping shape Bitcoin’s place in global affairs.
About Bitcoin 2025
The excitement is building as the world’s largest Bitcoin conference approaches, Bitcoin 2025. Set to take place in Las Vegas from May 27-29, this premier event is anticipated to draw Bitcoin enthusiasts, industry leaders, and innovators from all over the globe.
Be part of the revolution! Come experience the cultural movement that’s the Bitcoin Conference – a landmark event with wealth of opportunities for networking and learning. In 2025, Bitcoin takes over Las Vegas, uniting builders, leaders, and believers in the world’s most resilient monetary network.
New in 2025: Code & Country launches on Industry Day, bringing together policymakers, technologists, and industry leaders for a full day of focused collaboration.
The aim: strengthen Bitcoin’s role in national strategy, regulatory clarity, and technological sovereignty. This marks a new era where Bitcoin’s protocol and geopolitical potential intersect more directly than ever before.
Highlights Include
- Keynote Speakers: Renowned experts and visionaries will share their insights and predictions for the future of digital currency.
- Workshops and Panels: Attendees can participate in hands-on workshops and panel discussions covering a wide array of topics, from technical details to practical applications in various industries.
- Exhibition Hall: The exhibition will showcase art, cutting-edge products and services from top companies in the bitcoin ecosystem.
- Networking Opportunities: With thousands of attendees expected, Bitcoin 2025 offers unparalleled opportunities for networking with peers, potential partners, and thought leaders.
Keynote Speakers
The conference is set to feature an impressive lineup of speakers, including leading Bitcoin developers, experts, as well as influential figures from the financial sector. Topics range from the latest advancements to regulatory updates and investment strategies.
- JD Vance, Vice President Vance will become the first sitting vice president in the history of the United States to publicly voice his support for Bitcoin as he addresses the audience in Las Vegas.
- Ross Ulbricht, Freedom Advocate – Founder of the Silk Road marketplace, recently released by President Donald Trump from serving a double life sentence. His story has become emblematic of the clash between personal liberty, Bitcoin, and the state.
- Eric Trump & Donald Trump Jr, Both figures bring a bold voice to the conversation around Capitalism, Bitcoin, freedom, and economic sovereignty.
- Cameron & Tyler Winklevoss, Co-Founders of Gemini – Early Bitcoin adopters and founders of the regulated exchange Gemini.
- David Sacks, White House AI & Crypto Czar – Former PayPal COO and venture capitalist, now serving as the White House’s senior advisor on AI and cryptocurrency policy, leading national efforts on stablecoin legislation and digital asset strategy.
- Bryan Johnson, Founder of Project Blueprint – Tech entrepreneur and longevity researcher known for reversing his biological age and challenging fiat-era assumptions about health, time, and human potential.
Past Conferences in the USA
– 2021 Miami: Where President Nayib Bukele revealed plans for El Salvador to adopt Bitcoin as legal tender, making history live on stage. Attendance: 11,000
– 2022 Miami: Where Michael Saylor delivered a landmark address on corporate Bitcoin strategy and announced additional MicroStrategy purchases. Attendance: 26,000
– 2023 Miami: Where Secretary Robert F. Kennedy Jr. became the first U.S. presidential candidate to speak at a Bitcoin conference, addressing financial freedom and civil liberties. Attendance: 15,000
– 2024 Nashville: Highlights include President Donald J. Trump’s appearance, where he voiced support for Bitcoin mining and national monetary sovereignty. Attendance: 22,000Join Us in Las Vegas
- Date: May 27-29, 2025
- Venue: The Venetian, Las Vegas, NV, USA
- Tickets: https://b.tc/conference/2025
- Get a free General Admission ticket when you deposit $200 on eToro – while supplies last!
This post Nigel Farage To Speak At Bitcoin 2025 Conference first appeared on Bitcoin Magazine and is written by Conor Mulcahy.
-
 @ 26769dac:498e333b
2025-05-25 12:51:09
@ 26769dac:498e333b
2025-05-25 12:51:09Here's to the ones who can\ Feel there cause\ Surrender\ Change their ways\ But keep their fire\ And never give up
We will transform this world\ Restructuring\ One belief at a time
-
 @ daa41bed:88f54153
2025-02-09 16:50:04
@ daa41bed:88f54153
2025-02-09 16:50:04There has been a good bit of discussion on Nostr over the past few days about the merits of zaps as a method of engaging with notes, so after writing a rather lengthy article on the pros of a strategic Bitcoin reserve, I wanted to take some time to chime in on the much more fun topic of digital engagement.
Let's begin by defining a couple of things:
Nostr is a decentralized, censorship-resistance protocol whose current biggest use case is social media (think Twitter/X). Instead of relying on company servers, it relies on relays that anyone can spin up and own their own content. Its use cases are much bigger, though, and this article is hosted on my own relay, using my own Nostr relay as an example.
Zap is a tip or donation denominated in sats (small units of Bitcoin) sent from one user to another. This is generally done directly over the Lightning Network but is increasingly using Cashu tokens. For the sake of this discussion, how you transmit/receive zaps will be irrelevant, so don't worry if you don't know what Lightning or Cashu are.
If we look at how users engage with posts and follows/followers on platforms like Twitter, Facebook, etc., it becomes evident that traditional social media thrives on engagement farming. The more outrageous a post, the more likely it will get a reaction. We see a version of this on more visual social platforms like YouTube and TikTok that use carefully crafted thumbnail images to grab the user's attention to click the video. If you'd like to dive deep into the psychology and science behind social media engagement, let me know, and I'd be happy to follow up with another article.
In this user engagement model, a user is given the option to comment or like the original post, or share it among their followers to increase its signal. They receive no value from engaging with the content aside from the dopamine hit of the original experience or having their comment liked back by whatever influencer they provide value to. Ad revenue flows to the content creator. Clout flows to the content creator. Sales revenue from merch and content placement flows to the content creator. We call this a linear economy -- the idea that resources get created, used up, then thrown away. Users create content and farm as much engagement as possible, then the content is forgotten within a few hours as they move on to the next piece of content to be farmed.
What if there were a simple way to give value back to those who engage with your content? By implementing some value-for-value model -- a circular economy. Enter zaps.

Unlike traditional social media platforms, Nostr does not actively use algorithms to determine what content is popular, nor does it push content created for active user engagement to the top of a user's timeline. Yes, there are "trending" and "most zapped" timelines that users can choose to use as their default, but these use relatively straightforward engagement metrics to rank posts for these timelines.
That is not to say that we may not see clients actively seeking to refine timeline algorithms for specific metrics. Still, the beauty of having an open protocol with media that is controlled solely by its users is that users who begin to see their timeline gamed towards specific algorithms can choose to move to another client, and for those who are more tech-savvy, they can opt to run their own relays or create their own clients with personalized algorithms and web of trust scoring systems.
Zaps enable the means to create a new type of social media economy in which creators can earn for creating content and users can earn by actively engaging with it. Like and reposting content is relatively frictionless and costs nothing but a simple button tap. Zaps provide active engagement because they signal to your followers and those of the content creator that this post has genuine value, quite literally in the form of money—sats.

I have seen some comments on Nostr claiming that removing likes and reactions is for wealthy people who can afford to send zaps and that the majority of people in the US and around the world do not have the time or money to zap because they have better things to spend their money like feeding their families and paying their bills. While at face value, these may seem like valid arguments, they, unfortunately, represent the brainwashed, defeatist attitude that our current economic (and, by extension, social media) systems aim to instill in all of us to continue extracting value from our lives.
Imagine now, if those people dedicating their own time (time = money) to mine pity points on social media would instead spend that time with genuine value creation by posting content that is meaningful to cultural discussions. Imagine if, instead of complaining that their posts get no zaps and going on a tirade about how much of a victim they are, they would empower themselves to take control of their content and give value back to the world; where would that leave us? How much value could be created on a nascent platform such as Nostr, and how quickly could it overtake other platforms?
Other users argue about user experience and that additional friction (i.e., zaps) leads to lower engagement, as proven by decades of studies on user interaction. While the added friction may turn some users away, does that necessarily provide less value? I argue quite the opposite. You haven't made a few sats from zaps with your content? Can't afford to send some sats to a wallet for zapping? How about using the most excellent available resource and spending 10 seconds of your time to leave a comment? Likes and reactions are valueless transactions. Social media's real value derives from providing monetary compensation and actively engaging in a conversation with posts you find interesting or thought-provoking. Remember when humans thrived on conversation and discussion for entertainment instead of simply being an onlooker of someone else's life?
If you've made it this far, my only request is this: try only zapping and commenting as a method of engagement for two weeks. Sure, you may end up liking a post here and there, but be more mindful of how you interact with the world and break yourself from blind instinct. You'll thank me later.

-
 @ 3283ef81:0a531a33
2025-05-25 12:14:51
@ 3283ef81:0a531a33
2025-05-25 12:14:51Aliquam eu turpis sed enim ultricies scelerisque\ Duis posuere congue faucibus
Praesent pretium orci ante, et faucibus lectus euismod a
-
 @ f240be2b:00c761ba
2025-05-25 10:32:12
@ f240be2b:00c761ba
2025-05-25 10:32:12Wirtschaftswunder werden oft als mysteriöse, unvorhersehbare Phänomene dargestellt – als wären sie glückliche Zufälle oder das Ergebnis genialer Planungen. Bei näherer Betrachtung offenbart sich jedoch ein grundlegendes Muster: Diese vermeintlichen "Wunder" sind keine übernatürlichen Ereignisse, sondern das natürliche Ergebnis wirtschaftlicher Freiheit. Die Erfolgsgeschichten verschiedener Länder bestätigen diese These und zeigen, dass Wohlstand entsteht, wenn Menschen die Freiheit haben, zu handeln, zu produzieren und zu innovieren.
Das deutsche Wirtschaftswunder
Nach dem Zweiten Weltkrieg lag Deutschland in Trümmern. Die Industrieproduktion war auf ein Viertel des Vorkriegsniveaus gesunken, und Millionen Menschen lebten in Armut. Doch innerhalb weniger Jahre erlebte Westdeutschland einen beispiellosen wirtschaftlichen Aufschwung, der als "Wirtschaftswunder" in die Geschichte einging.
Der Wandel begann mit Ludwig Erhards mutiger Währungsreform und Preisfreigabe im Jahr 1948. Erhard, damals Direktor der Wirtschaftsverwaltung, schaffte Preiskontrollen ab und führte die Deutsche Mark ein. Diese Maßnahmen wurden von Besatzungsmächten und deutschen Sozialisten skeptisch betrachtet und waren zunächst unpopulär. Doch die Ergebnisse sprachen für sich: Über Nacht füllten sich die Ladenregale wieder, und die Schwarzmärkte verschwanden.
Das Kernprinzip war einfach: Erhard gab den Menschen ihre wirtschaftliche Freiheit zurück. Er schuf einen stabilen Rechtsrahmen, reduzierte staatliche Eingriffe und förderte den freien Wettbewerb. Die Sozialisten bekämpften diese Entwicklung von Anfang an, deuteten diese jedoch im Nachhinein als “soziale Marktwirtschaft” um, diese Lüge verbreiten sie noch heute sehr erfolgreich.
Die freie Marktwirtschaft erlaubte es den Deutschen, ihre unternehmerischen Fähigkeiten zu entfalten und ihre zerstörte Wirtschaft wieder aufzubauen.\ Das Ergebnis: Zwischen 1950 und 1960 wuchs das westdeutsche BIP um mehr als 8% jährlich. Die Arbeitslosigkeit sank von 11% auf unter 1%, und Deutschland wurde zu einer der führenden Exportnationen der Welt. Was als "Wunder" bezeichnet wurde, war tatsächlich die natürliche Konsequenz wiederhergestellter wirtschaftlicher Freiheit.
Chiles wirtschaftliche Transformation
Chile bietet ein weiteres eindrucksvolles Beispiel. In den frühen 1970er Jahren litt das Land unter einer Hyperinflation von 700%, einem schrumpfenden BIP und zunehmender Armut. Die Transformation begann in den späten 1970er Jahren mit tiefgreifenden Wirtschaftsreformen.
Die chilenische Regierung privatisierte Staatsunternehmen, öffnete Märkte für internationalen Handel, schuf ein stabiles Finanzsystem und führte ein innovatives Rentensystem ein. Während andere lateinamerikanische Länder mit protektionistischen Maßnahmen experimentierten, entschied sich Chile für wirtschaftliche Freiheit.
Die Ergebnisse waren beeindruckend: Zwischen 1975 und 2000 verdreifachte sich Chiles Pro-Kopf-Einkommen. Die Armutsquote sank von 45% auf unter 10%. Heute hat Chile das höchste Pro-Kopf-Einkommen in Südamerika und eine der stabilsten Wirtschaften der Region.
Mit einer gewissen Melancholie müssen wir beobachten, wie die hart erkämpften Errungenschaften Chiles allmählich in den Schatten der Vergänglichkeit gleiten. Was einst als Leuchtturm wirtschaftlicher Transformation strahlte, wird nun von den Nebeln der kollektiven Amnesie umhüllt. In dieser Dämmerung der Erinnerung finden interventionistische Strömungen erneut fruchtbaren Boden.
Dieses Phänomen ist nicht auf Chile beschränkt. Auch in Deutschland verblasst die Erinnerung an die transformative Kraft der freien Marktwirtschaft. Die Geschichte wird umgedichtet, in der wirtschaftliche Freiheit als unbarmherziger Kapitalismus karikiert wird, während staatliche Intervention als einziger Weg zur sozialen Gerechtigkeit glorifiziert wird.
Chinas große Öffnung
Im Reich der Mitte vollzog sich die vielleicht dramatischste wirtschaftliche Metamorphose unserer Zeit. Nach Jahrzehnten der Isolation und planwirtschaftlicher Starrheit öffnete China unter Deng Xiaoping vorsichtig die Tore zur wirtschaftlichen Freiheit.
Die Transformation begann in den Reisfeldern, wo Bauern erstmals seit Generationen über ihre eigene Ernte bestimmen durften. Sie setzte sich fort in den pulsierenden Sonderwirtschaftszonen, wo unternehmerische Energie auf globale Märkte traf.
Das Ergebnis war atemberaubend: Fast vier Jahrzehnte mit durchschnittlich 10 Prozent Wirtschaftswachstum jährlich – eine beispiellose Leistung in der Wirtschaftsgeschichte. Mehr als 800 Millionen Menschen überwanden die Armut und fanden den Weg in die globale Mittelschicht. Selbst die partielle Einführung wirtschaftlicher Freiheiten entfesselte eine Produktivität, die die Welt veränderte.
Die zeitlose Lektion
Das Geheimnis wirtschaftlicher Erneuerung liegt nicht in komplexen Theorien oder staatlichen Eingriffen, sondern in der einfachen Weisheit, Menschen die Freiheit zu geben, ihre Träume zu verwirklichen. Wenn wir von "Wirtschaftswundern" sprechen, verkennen wir die wahre Natur dieser Transformationen.
Sie sind keine mysteriösen Anomalien, sondern vielmehr Bestätigungen eines zeitlosen Prinzips: In der fruchtbaren Erde wirtschaftlicher Freiheit blüht der menschliche Erfindungsgeist. Diese Erkenntnis ist keine ideologische Position, sondern eine durch die Geschichte vielfach bestätigte Wahrheit.
Die Lektion dieser Erfolgsgeschichten ist sowohl schlicht als auch tiefgründig: Der Weg zu Wohlstand und menschlicher Entfaltung führt über die Anerkennung und den Schutz wirtschaftlicher Freiheiten. In dieser Erkenntnis liegt vielleicht das wahre Wunder – die beständige Kraft einer einfachen Idee, die immer wieder Leben und Hoffnung in die dunkelsten wirtschaftlichen Landschaften bringt.
Der aufsteigende Stern des Südens
Jenseits der Andenkette, wo Argentinien und Chile ihre lange Grenze teilen, entfaltet sich eine neue Erfolgsgeschichte. Mit mutigen Reformen und einer Rückbesinnung auf wirtschaftliche Freiheit erwacht dieses Land mit viel Potenzial aus seinem langen Schlummer. Was wir beobachten, ist nichts weniger als die Geburt eines neuen südamerikanischen Wirtschaftswunders – geboren aus der Erkenntnis, dass Wohlstand nicht verteilt, sondern erschaffen wird.
-
 @ c9badfea:610f861a
2025-05-26 16:14:46
@ c9badfea:610f861a
2025-05-26 16:14:46- Install Trail Sense (it's free and open source)
- Open the app, and tap Next then I Agree
- Allow location access While Using The App and Allow notifications
- Tap 🧭 on the bottom bar to open the compass
- Use 📍️ in the upper left to manage paths
- Use 🗺️ in the upper right to take a picture of a physical map and navigate on it
- Use ⬆️ in the lower right to set beacons along your hike
- Tap ☁️ on the bottom bar for weather information
- Use ☁️ in the upper left to predict weather using cloud patterns
- Use 🌡️ in the upper right to estimate the temperature (useful when in the mountains)
- Tap ✨ on the bottom bar for astronomy details
- Use 🔦 in the upper left to toggle your phone's flashlight
- Use ⬇️ in the upper right to set alarms and reminders (e.g. sunset alerts)
- Tap ▦ on the bottom bar to access extra tools
- Use 🔦 to toggle the flashlight
- Use 🔊 to play a whistle sound
- Use 🔋 to turn battery-saving mode on or off
- Select User Guide for help with all features
- Enjoy!
ℹ️ Explore the app - it has many features worth learning
-
 @ 9e69e420:d12360c2
2025-02-01 11:16:04
@ 9e69e420:d12360c2
2025-02-01 11:16:04Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.

CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language.
One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse.
-
 @ 86dfbe73:628cef55
2025-05-25 08:20:07
@ 86dfbe73:628cef55
2025-05-25 08:20:07Robustheit ist die Eigenschaft eines Systems, auch unter schwierigen Bedingungen funktionieren zu können: trotz Störungen und einer gewissen Verschlechterung seiner internen Prozesse. Das Leben als Ganzes ist robust. Dasselbe gilt für Ökosysteme: Sie können den Verlust einiger Arten überstehen und sich an veränderte Umweltbedingungen anpassen.
Der Hauptfeind der Robustheit ist das Streben nach Effizienz. Ein auf Effizienz optimiertes System hat keine Reserven mehr, sich an Störungen anzupassen. Es wird fragil. Wir optimieren die Gesellschaft und ihre Subsysteme (z. B. Institutionen) seit 5000 Jahren auf Wachstum, Effizienz und Produktivität. Und wir haben das Optimierungstempo mit den beiden Turbo-Boosts fossile Brennstoffe und Informationstechnologie beschleunigt. Deshalb ist alles um uns herum fragil geworden. Beispielsweise kann ein Virusausbruch in China sich zu einer Pandemie entwickeln, weil die Menschen weit und schnell reisen können und müssen.
Robustheit ist nicht absolut und dauerhaft. Ein System kann durch Störungen, die zu gravierend für es sind, fragil werden. Ehemals robuste Ökosysteme wie Regenwälder wurden durch menschliche Ausbeutung fragil. Deregulierung hat sowohl Regierungen als auch die Wirtschaft effizienter gemacht, allerdings zum Preis zunehmender Fragilität. Unternehmen sind mächtiger geworden als viele Staaten, was bedeutet, dass demokratisch gewählte Parlamente und Regierungen nicht mehr die Kontrolle haben. Heute kann eine einzelne Person demokratische Wahlen weltweit manipulieren, indem sie ein soziales Netzwerk kontrolliert. Das ist Fragilität pur.
Wir müssen als Gesellschaft die Effizienz in den Hintergrund rücken und uns mehr auf Robustheit konzentrieren.
-
 @ 97c70a44:ad98e322
2025-01-30 17:15:37
@ 97c70a44:ad98e322
2025-01-30 17:15:37There was a slight dust up recently over a website someone runs removing a listing for an app someone built based on entirely arbitrary criteria. I'm not to going to attempt to speak for either wounded party, but I would like to share my own personal definition for what constitutes a "nostr app" in an effort to help clarify what might be an otherwise confusing and opaque purity test.
In this post, I will be committing the "no true Scotsman" fallacy, in which I start with the most liberal definition I can come up with, and gradually refine it until all that is left is the purest, gleamingest, most imaginary and unattainable nostr app imaginable. As I write this, I wonder if anything built yet will actually qualify. In any case, here we go.
It uses nostr
The lowest bar for what a "nostr app" might be is an app ("application" - i.e. software, not necessarily a native app of any kind) that has some nostr-specific code in it, but which doesn't take any advantage of what makes nostr distinctive as a protocol.
Examples might include a scraper of some kind which fulfills its charter by fetching data from relays (regardless of whether it validates or retains signatures). Another might be a regular web 2.0 app which provides an option to "log in with nostr" by requesting and storing the user's public key.
In either case, the fact that nostr is involved is entirely neutral. A scraper can scrape html, pdfs, jsonl, whatever data source - nostr relays are just another target. Likewise, a user's key in this scenario is treated merely as an opaque identifier, with no appreciation for the super powers it brings along.
In most cases, this kind of app only exists as a marketing ploy, or less cynically, because it wants to get in on the hype of being a "nostr app", without the developer quite understanding what that means, or having the budget to execute properly on the claim.
It leverages nostr
Some of you might be wondering, "isn't 'leverage' a synonym for 'use'?" And you would be right, but for one connotative difference. It's possible to "use" something improperly, but by definition leverage gives you a mechanical advantage that you wouldn't otherwise have. This is the second category of "nostr app".
This kind of app gets some benefit out of the nostr protocol and network, but in an entirely selfish fashion. The intention of this kind of app is not to augment the nostr network, but to augment its own UX by borrowing some nifty thing from the protocol without really contributing anything back.
Some examples might include:
- Using nostr signers to encrypt or sign data, and then store that data on a proprietary server.
- Using nostr relays as a kind of low-code backend, but using proprietary event payloads.
- Using nostr event kinds to represent data (why), but not leveraging the trustlessness that buys you.
An application in this category might even communicate to its users via nostr DMs - but this doesn't make it a "nostr app" any more than a website that emails you hot deals on herbal supplements is an "email app". These apps are purely parasitic on the nostr ecosystem.
In the long-term, that's not necessarily a bad thing. Email's ubiquity is self-reinforcing. But in the short term, this kind of "nostr app" can actually do damage to nostr's reputation by over-promising and under-delivering.
It complements nostr
Next up, we have apps that get some benefit out of nostr as above, but give back by providing a unique value proposition to nostr users as nostr users. This is a bit of a fine distinction, but for me this category is for apps which focus on solving problems that nostr isn't good at solving, leaving the nostr integration in a secondary or supporting role.
One example of this kind of app was Mutiny (RIP), which not only allowed users to sign in with nostr, but also pulled those users' social graphs so that users could send money to people they knew and trusted. Mutiny was doing a great job of leveraging nostr, as well as providing value to users with nostr identities - but it was still primarily a bitcoin wallet, not a "nostr app" in the purest sense.
Other examples are things like Nostr Nests and Zap.stream, whose core value proposition is streaming video or audio content. Both make great use of nostr identities, data formats, and relays, but they're primarily streaming apps. A good litmus test for things like this is: if you got rid of nostr, would it be the same product (even if inferior in certain ways)?
A similar category is infrastructure providers that benefit nostr by their existence (and may in fact be targeted explicitly at nostr users), but do things in a centralized, old-web way; for example: media hosts, DNS registrars, hosting providers, and CDNs.
To be clear here, I'm not casting aspersions (I don't even know what those are, or where to buy them). All the apps mentioned above use nostr to great effect, and are a real benefit to nostr users. But they are not True Scotsmen.
It embodies nostr
Ok, here we go. This is the crème de la crème, the top du top, the meilleur du meilleur, the bee's knees. The purest, holiest, most chaste category of nostr app out there. The apps which are, indeed, nostr indigitate.
This category of nostr app (see, no quotes this time) can be defined by the converse of the previous category. If nostr was removed from this type of application, would it be impossible to create the same product?
To tease this apart a bit, apps that leverage the technical aspects of nostr are dependent on nostr the protocol, while apps that benefit nostr exclusively via network effect are integrated into nostr the network. An app that does both things is working in symbiosis with nostr as a whole.
An app that embraces both nostr's protocol and its network becomes an organic extension of every other nostr app out there, multiplying both its competitive moat and its contribution to the ecosystem:
- In contrast to apps that only borrow from nostr on the technical level but continue to operate in their own silos, an application integrated into the nostr network comes pre-packaged with existing users, and is able to provide more value to those users because of other nostr products. On nostr, it's a good thing to advertise your competitors.
- In contrast to apps that only market themselves to nostr users without building out a deep integration on the protocol level, a deeply integrated app becomes an asset to every other nostr app by becoming an organic extension of them through interoperability. This results in increased traffic to the app as other developers and users refer people to it instead of solving their problem on their own. This is the "micro-apps" utopia we've all been waiting for.
Credible exit doesn't matter if there aren't alternative services. Interoperability is pointless if other applications don't offer something your app doesn't. Marketing to nostr users doesn't matter if you don't augment their agency as nostr users.
If I had to choose a single NIP that represents the mindset behind this kind of app, it would be NIP 89 A.K.A. "Recommended Application Handlers", which states:
Nostr's discoverability and transparent event interaction is one of its most interesting/novel mechanics. This NIP provides a simple way for clients to discover applications that handle events of a specific kind to ensure smooth cross-client and cross-kind interactions.
These handlers are the glue that holds nostr apps together. A single event, signed by the developer of an application (or by the application's own account) tells anyone who wants to know 1. what event kinds the app supports, 2. how to link to the app (if it's a client), and (if the pubkey also publishes a kind 10002), 3. which relays the app prefers.
As a sidenote, NIP 89 is currently focused more on clients, leaving DVMs, relays, signers, etc somewhat out in the cold. Updating 89 to include tailored listings for each kind of supporting app would be a huge improvement to the protocol. This, plus a good front end for navigating these listings (sorry nostrapp.link, close but no cigar) would obviate the evil centralized websites that curate apps based on arbitrary criteria.
Examples of this kind of app obviously include many kind 1 clients, as well as clients that attempt to bring the benefits of the nostr protocol and network to new use cases - whether long form content, video, image posts, music, emojis, recipes, project management, or any other "content type".
To drill down into one example, let's think for a moment about forms. What's so great about a forms app that is built on nostr? Well,
- There is a spec for forms and responses, which means that...
- Multiple clients can implement the same data format, allowing for credible exit and user choice, even of...
- Other products not focused on forms, which can still view, respond to, or embed forms, and which can send their users via NIP 89 to a client that does...
- Cryptographically sign forms and responses, which means they are self-authenticating and can be sent to...
- Multiple relays, which reduces the amount of trust necessary to be confident results haven't been deliberately "lost".
Show me a forms product that does all of those things, and isn't built on nostr. You can't, because it doesn't exist. Meanwhile, there are plenty of image hosts with APIs, streaming services, and bitcoin wallets which have basically the same levels of censorship resistance, interoperability, and network effect as if they weren't built on nostr.
It supports nostr
Notice I haven't said anything about whether relays, signers, blossom servers, software libraries, DVMs, and the accumulated addenda of the nostr ecosystem are nostr apps. Well, they are (usually).
This is the category of nostr app that gets none of the credit for doing all of the work. There's no question that they qualify as beautiful nostrcorns, because their value propositions are entirely meaningless outside of the context of nostr. Who needs a signer if you don't have a cryptographic identity you need to protect? DVMs are literally impossible to use without relays. How are you going to find the blossom server that will serve a given hash if you don't know which servers the publishing user has selected to store their content?
In addition to being entirely contextualized by nostr architecture, this type of nostr app is valuable because it does things "the nostr way". By that I mean that they don't simply try to replicate existing internet functionality into a nostr context; instead, they create entirely new ways of putting the basic building blocks of the internet back together.
A great example of this is how Nostr Connect, Nostr Wallet Connect, and DVMs all use relays as brokers, which allows service providers to avoid having to accept incoming network connections. This opens up really interesting possibilities all on its own.
So while I might hesitate to call many of these things "apps", they are certainly "nostr".
Appendix: it smells like a NINO
So, let's say you've created an app, but when you show it to people they politely smile, nod, and call it a NINO (Nostr In Name Only). What's a hacker to do? Well, here's your handy-dandy guide on how to wash that NINO stench off and Become a Nostr.
You app might be a NINO if:
- There's no NIP for your data format (or you're abusing NIP 78, 32, etc by inventing a sub-protocol inside an existing event kind)
- There's a NIP, but no one knows about it because it's in a text file on your hard drive (or buried in your project's repository)
- Your NIP imposes an incompatible/centralized/legacy web paradigm onto nostr
- Your NIP relies on trusted third (or first) parties
- There's only one implementation of your NIP (yours)
- Your core value proposition doesn't depend on relays, events, or nostr identities
- One or more relay urls are hard-coded into the source code
- Your app depends on a specific relay implementation to work (ahem, relay29)
- You don't validate event signatures
- You don't publish events to relays you don't control
- You don't read events from relays you don't control
- You use legacy web services to solve problems, rather than nostr-native solutions
- You use nostr-native solutions, but you've hardcoded their pubkeys or URLs into your app
- You don't use NIP 89 to discover clients and services
- You haven't published a NIP 89 listing for your app
- You don't leverage your users' web of trust for filtering out spam
- You don't respect your users' mute lists
- You try to "own" your users' data
Now let me just re-iterate - it's ok to be a NINO. We need NINOs, because nostr can't (and shouldn't) tackle every problem. You just need to decide whether your app, as a NINO, is actually contributing to the nostr ecosystem, or whether you're just using buzzwords to whitewash a legacy web software product.
If you're in the former camp, great! If you're in the latter, what are you waiting for? Only you can fix your NINO problem. And there are lots of ways to do this, depending on your own unique situation:
- Drop nostr support if it's not doing anyone any good. If you want to build a normal company and make some money, that's perfectly fine.
- Build out your nostr integration - start taking advantage of webs of trust, self-authenticating data, event handlers, etc.
- Work around the problem. Think you need a special relay feature for your app to work? Guess again. Consider encryption, AUTH, DVMs, or better data formats.
- Think your idea is a good one? Talk to other devs or open a PR to the nips repo. No one can adopt your NIP if they don't know about it.
- Keep going. It can sometimes be hard to distinguish a research project from a NINO. New ideas have to be built out before they can be fully appreciated.
- Listen to advice. Nostr developers are friendly and happy to help. If you're not sure why you're getting traction, ask!
I sincerely hope this article is useful for all of you out there in NINO land. Maybe this made you feel better about not passing the totally optional nostr app purity test. Or maybe it gave you some actionable next steps towards making a great NINON (Nostr In Not Only Name) app. In either case, GM and PV.
-
 @ 5c26ee8b:a4d229aa
2025-05-26 16:10:05
@ 5c26ee8b:a4d229aa
2025-05-26 16:10:05In March 2022, I have introduced “VCPs”; (Virtual Currency points). So that the international transactions are made without relying on one currency or another and the financial crises are easily avoided.
You may have noticed that banks are increasing their gold reserves and that there are interests for local virtual currency and that was after the note was published.
The picture of the note showing its date will be in attachment to this post; I can’t edit it to avoid that its date gets changed. Here its content:
Conversion of international banking system: The “VCPs” system: * Each central bank would keep its assets and funds in homeland. * Establishing the value of one virtual currency point. I suggested that: 1 virtual currency point (VCP) = 0.1 gram of gold. * Virtual evaluation must be made to each currency, virtual currency points must be added to each currency’s market value. * International transfers and payments must use the virtual currency points, VCPs, assigned to each currency in international operations. * Daily, weekly, monthly or yearly the actual money corresponding to the virtual currency points used in payments and transfers will be sent by any chosen mean of transport to the banks that had completed the operations or to the corresponding central banks. In this way no currency would prevail in international payments as all currencies will be considered as VCPs. —————————————————————- Because of the need of more guidelines to start using VCPs I have published the following updates:
VCPs allowance updates:
- Not only gold, also precious stones or agreed minerals held in banks can be used to obtain the VCPs allowance (public VCPs allowances). At the same time what is registered and kept in circulation (of gold, precious stones and agreed minerals that belongs to the people) in the country as private VCPs allowances to increase the VCPs allowances. The people can use their personal VCPs along with their precious items for purchases; for example if they sell or use their own gold to buy something, they must give their VCPs registration receipt or card (if they didn’t register their gold to obtain VCPs allowance, they can get it registered at the moment they decide to sell it so it gets added to the private VCPs allowances of his/her country). However, the registered materials must be declared at all borders while traveling once exceeded an internationally agreed specific amount (such as the value of €10000). Therefore a registration method can be agreed with gold and jewelry shops. For instance, while evaluating the materials getting registered, an online VCPs account (for a first registration) can get made on the site that is getting ready and the registration can be combined with a physical/online card (VCPs allowance card. For registering other materials in a later moment, the same card can be used to access the same account. Note that the materials must be used with the private VCPs allowance card for buying or selling, while for public VCPs accounts it’s not necessary because the materials will be kept in the central bank or other banks) or a receipt with a serial number (and other methods to protect customers from fraud). Banks can buy private VCPs while buying gold or other agreed materials and make them public VCPs. And people can have public VCPs allowances corresponding to the value of money (currency) they have already in their accounts. While if people buy gold from the bank (with cash or any other payment method), the related public VCPs allowance will be transformed into private ones (the buyers must receive the actual gold with the private VCPs allowance).
- The agreed materials that can be used to obtain public VCPs must not be consumable (such as oil or natural gas) or used for industrial purposes (such as iron or lithium).
- The printed and online (used by credit or debit cards) currency kept in circulation of the concerned country must correspond to the value of public VCPs allowance that must correspond with the value of gold kept in the central bank (printing more money will decrease its own value internationally).
- Private banks in the same country can have a public VCPs agreement with the central bank so that each bank registers and declares how much gold or valuable materials it has and get its own share of public VCPs allowance and its related printed/online currency in circulation.
- Gems and gold kept in museums can have public VCPs allowances that correspond to their weights only not the archeological values.
- International trade can use public VCPs allowances and the physical payment must follow; either by a preferred currency or gold. However if two or more countries have a trade agreement they can barter goods using IVCPs (International VCPs Allowances; that does not need to have a deposited amount of gold although they will use the same reference as public or private VCPs because it’s a general way to evaluate goods of different types; so for example oil can be swapped for electronics based on how much IVCPs are agreed to be equally swapped each year; i.e. a gallon of oil that costs 50 IVCPs can be swapped for a device that costs 25 IVCPs and grains that cost 25 IVCPs in an International VCPs Allowance Agreement where all parties receives the agreed goods without transferring money or gold). The amount of IVCPs can be agreed per year or there could a multiple online account/s viewable by the countries/parties taking part in the agreement showing the balance of International VCPs that can still be used in bartering goods for each one of the participating countries/parties).
- Cryptocurrencies can be like International VCPs they won’t need to have a deposit of gold, however they must go through an evaluation process compared to their current comparative value and gold (i.e. the amount of bitcoin that must be paid to buy a 0.1g of gold now can become the fixed value) so that the Cryptocurrencies can still be used for trading or bartering for goods even after the release of VCPs. The Cryptocurrencies can sustain the deficiencies of amount of currency that can be used in the same country or internationally (because not everyone can have enough gold deposited to sustain the daily trade). However regulations on the amount of Cryptocurrency/ies exchanged in a country must be agreed with its own central bank or there could be an international agreement; this amount can’t be less than what’s already in use of a certain Cryptocurrency. Or Cryptocurrencies can be exchanged with IVCPs (to protect people’s money while keeping in mind their compared value with gold now) and an amount of International VCPs allowance can be used also for bartering goods in the same country through an agreement with its own central bank.
- Public VCPs must have printable cash allowance that can be in the country or overseas (registered in banks, exchange companies and at borders). Each bank can have registers of local or foreign cash.
- In order to avoid the devaluation of the currency, because the printed money will corrisponde to the gold or valuable minerals held by the country, the concerned country must retrieve the cash abroad and replace it either with another currency or IVCPs through a trade agreement.
- To compensate the deficit of VCPs necessary for daily use within a country and to make a proper distinction, locally, Local Virtual Points (LVCPs) can be used.
- The Local VCPs would be issued by local authorities.
Meanwhile, countries started using the free VCPs platform that is built by a talented web developer in JavaScript; fiatjaf. I insist though that the trade name for the virtual currency points stays “VCPs” and that the clients are made aware of its usage in their daily banking.
-
 @ 8d34bd24:414be32b
2025-05-25 06:29:21
@ 8d34bd24:414be32b
2025-05-25 06:29:21It seems like most Christians today have lost their reverence and awe of God. We’ve attributed God’s awesome creation by the word of His mouth to random chance and a Big Bang. We’ve attributed the many layers of sediment to millions and billions of years of time instead of God’s judgment of evil. We’ve emphasized His love and mercy to the point that we’ve forgotten about His holiness and righteous wrath. We’ve brought God down to our level and made Him either our “buddy” or made Him our magic genie servant, who is just there to answer our every want and whim.
The God of the Bible is a holy and awesome God who should be both loved and feared.
The fear of the Lord is the beginning of knowledge;\ Fools despise wisdom and instruction. (Proverbs 1:7)
The God of the Bible is the Lord of Lords and King of Kings who “… upholds all things by the word of His power. …” (Hebrews 1:3). Yes, God loves us as sons. Yes, God is merciful. Yes, through Jesus we have the blessed opportunity to approach God directly. None of that means we get to treat God like just another friend. We are to approach God with fear and trembling and worship Him in reverence and awe.
Worship the Lord with reverence And rejoice with trembling. (Psalm 2:11)
Part of the problem is that our culture just doesn’t show reverence to authority. It focuses on self and freedom. The whole thought of reverence for authority is incomprehensible for many. Look at this Psalm of worship:
The Lord reigns, let the peoples tremble;\ He is enthroned above the cherubim, let the earth shake!\ The Lord is great in Zion,\ And He is exalted above all the peoples.\ Let them praise Your great and awesome name;\ Holy is He. (Psalm 99:1-3)
This is the way we should view God and the proper attitude for approaching God.
Another issue is that we don’t study what God has done in the past. In the Old Testament, God commanded the Israelites to setup monuments of remembrance and to teach their kids all of the great things God had done for them. When they failed to do so, Israel drifted astray.
You shall teach them to your sons, talking of them when you sit in your house and when you walk along the road and when you lie down and when you rise up. (Deuteronomy 11:19)
God has given us the Bible, His word, so that we can know Him, know His character, and know His great deeds. When we fail to be in His word daily, we can forget (or not even know) the greatness of our God.
Establish Your word to Your servant,\ As that which produces reverence for You. (Psalm 119:38)
Do you love God’s word like this? Do you hunger for God’s word? Do you seek to know everything about God that you can know? When we love someone or something, we want to know everything about it.
Princes persecute me without cause,\ But my heart stands in awe of Your words.\ **I rejoice at Your word,\ As one who finds great spoil. \ (Psalm 119:161-162) {emphasis mine}
In addition to what we can learn about God in the Bible, we also need to remember what God has done in our own lives. We need to dwell on what God has done for us. We can just try to remember. Even better (I’ll admit this is a weakness for me), write down answered prayers, blessings, and other things God has done for you. My son has been writing down one blessing every day for over a year. What an example he is!
After we have thought about what God has done for us and those we care about, we should praise Him for His great works.
Shout joyfully to God, all the earth;\ Sing the glory of His name;\ Make His praise glorious.\ Say to God, “How awesome are Your works!\ Because of the greatness of Your power \ Your enemies will give feigned obedience to You.\ All the earth will worship You,\ And will sing praises to You;\ They will sing praises to Your name.” Selah.\ **Come and see the works of God,\ Who is awesome in His deeds toward the sons of men. \ (Psalm 66:1-5) {emphasis mine}
There is nothing we can do to earn salvation from God, but we should be in awe of what He has done for us leading to submission and obedience in gratitude.
Therefore, since we receive a kingdom which cannot be shaken, let us show gratitude, by which we may offer to God an acceptable service with reverence and awe; for our God is a consuming fire. (Hebrews 12:28-29) {emphasis mine}
Are you thankful for your blessings or resentful for what you don’t have? Do you worship God or take things He has provided for granted? Do you tell the world the awesome things God has done for you or do you stay silent? Do you claim to be a Christian, but live a life no different than those around you?
Then the Lord said,
“Because this people draw near with their words\ And honor Me with their lip service,\ But they remove their hearts far from Me,\ And their reverence for Me consists of tradition learned by rote, (Isaiah 29:13)
I hope this passage does not describe your relation ship with our awesome God. He deserves so much more. Instead we should be zealous to praise God and share His goodness with those around us.
Who is there to harm you if you prove zealous for what is good? But even if you should suffer for the sake of righteousness, you are blessed. And do not fear their intimidation, and do not be troubled, but sanctify Christ as Lord in your hearts, always being ready to make a defense to everyone who asks you to give an account for the hope that is in you, yet with gentleness and reverence; (1 Peter 3:13-15) {emphasis mine}
Did you know that you can even show reverence by your every day work?
By faith Noah, being warned by God about things not yet seen, in reverence prepared an ark for the salvation of his household, by which he condemned the world, and became an heir of the righteousness which is according to faith. (Hebrews 11:7) {emphasis mine}
When Noah stepped out in faith and obedience to God and built the ark as God commanded, despite the fact that the people around him probably thought he was crazy building a boat on dry ground that had never flooded, his work was a kind of reverence to God. Are there areas in your life where you can obey God in reverence to His awesomeness? Do you realize that quality work in obedience to God can be a form of worship?
Just going above and beyond in your job can be a form of worship of God if you are working extra hard to honor Him. Obedience is another form of worship and reverence.
Then Zerubbabel the son of Shealtiel, and Joshua the son of Jehozadak, the high priest, with all the remnant of the people, obeyed the voice of the Lord their God and the words of Haggai the prophet, as the Lord their God had sent him. And the people showed reverence for the Lord. (Haggai 1:12) {emphasis mine}
Too many people have put the word of men (especially scientists) above the word of God and have tried to change the clear meaning of the Bible. I used to think it strange how the Bible goes through the days of creation and ends each day with “and there was evening and there was morning, the xth day.” Since a day has an evening and a morning, that seemed redundant. Why did God speak in this manner? God knew that a day would come when many scientist would try to disprove God and would claim that these days were not 24 hour days, but long ages. When a writer is trying to convey long ages, the writer does not mention evening/morning and doesn’t count the days.1
When we no longer see God as speaking the universe and everything in it into existence, we tend to not see God as an awesome God. We don’t see His power. We don’t see His knowledge. We don’t see His goodness. We also don’t see His authority. Why do we have to obey God? Because He created us and because He upholds us. Without Him we would not exist. Our creator has the authority to command His creation. When we compromise in this area, we lose our submission, our awe, and our reverence. (For more on the subject see my series.) When we believe His great works, especially those spoken of in Genesis 1-11 and in Exodus, we can’t help but be in awe of our God.
For the word of the Lord is upright,\ And all His work is done in faithfulness.\ He loves righteousness and justice;\ The earth is full of the lovingkindness of the Lord.\ By the word of the Lord the heavens were made,\ And by the breath of His mouth all their host.\ He gathers the waters of the sea together as a heap;\ He lays up the deeps in storehouses.\ **Let all the earth fear the Lord;\ Let all the inhabitants of the world stand in awe of Him. \ (Psalm 33:4-8) {emphasis mine}
Remembering God’s great works, we can’t help but worship in awe and reverence.
By awesome deeds You answer us in righteousness, O God of our salvation,\ *You who are the trust of all the ends of the earth* and of the farthest sea;\ Who establishes the mountains by His strength,\ Being girded with might;\ Who stills the roaring of the seas,\ The roaring of their waves,\ And the tumult of the peoples.\ They who dwell in the ends of the earth stand in awe of Your signs;\ You make the dawn and the sunset shout for joy. \ (Psalm 65:5-8) {emphasis mine}
If we truly do have awe and reverence for our God, we should be emboldened to tell those around us of His great works.
I will tell of Your name to my brethren;\ In the midst of the assembly I will praise You.\ You who fear the Lord, praise Him;\ All you descendants of Jacob, glorify Him,\ And stand in awe of Him, all you descendants of Israel. \ (Psalm 22:22-23) {emphasis mine}
May God grant you the wisdom to see His awesomeness and to trust Him, serve Him, obey Him, and worship Him as He so rightly deserves. May you always have a right view of God and a hunger for His word and a personal relationship with Him. To God be the Glory!
Trust Jesus
FYI, these are a few more passages on the subject that are helpful, but didn’t fit in the flow of my post.
Great is the Lord, and highly to be praised,\ And His greatness is unsearchable.\ One generation shall praise Your works to another,\ And shall declare Your mighty acts.\ On the glorious splendor of Your majesty\ And on Your wonderful works, I will meditate.\ Men shall speak of the power of Your awesome acts,\ And I will tell of Your greatness. (Psalm 145:3-6)
The boastful shall not stand before Your eyes;\ You hate all who do iniquity.\ You destroy those who speak falsehood;\ The Lord abhors the man of bloodshed and deceit.\ But as for me, by Your abundant lovingkindness I will enter Your house,\ At Your holy temple I will bow in reverence for You. (Psalm 5:5-7) {emphasis mine}
If you do not listen, and if you do not take it to heart to give honor to My name,” says the Lord of hosts, “then I will send the curse upon you and I will curse your blessings; and indeed, I have cursed them already, because you are not taking it to heart. Behold, I am going to rebuke your offspring, and I will spread refuse on your faces, the refuse of your feasts; and you will be taken away with it. Then you will know that I have sent this commandment to you, that My covenant may continue with Levi,” says the Lord of hosts. “My covenant with him was one of life and peace, and I gave them to him as an object of reverence; so he revered Me and stood in awe of My name. (Malachi 2:2-5) {emphasis mine}
-
 @ 9e69e420:d12360c2
2025-01-30 12:23:04
@ 9e69e420:d12360c2
2025-01-30 12:23:04Tech stocks have taken a hit globally after China's DeepSeek launched a competitive AI chatbot at a much lower cost than US counterparts. This has stirred market fears of a $1.2 trillion loss across tech companies when trading opens in New York.
DeepSeek’s chatbot quickly topped download charts and surprised experts with its capabilities, developed for only $5.6 million.
The Nasdaq dropped over 3% in premarket trading, with major firms like Nvidia falling more than 10%. SoftBank also saw losses shortly after investing in a significant US AI venture.
Venture capitalist Marc Andreessen called it “AI’s Sputnik moment,” highlighting its potential impact on the industry.
![] (https://www.telegraph.co.uk/content/dam/business/2025/01/27/TELEMMGLPICT000409807198_17379939060750_trans_NvBQzQNjv4BqgsaO8O78rhmZrDxTlQBjdGLvJF5WfpqnBZShRL_tOZw.jpeg)
-
 @ bf47c19e:c3d2573b
2025-05-26 14:53:12
@ bf47c19e:c3d2573b
2025-05-26 14:53:12Originalni tekst na bitcoin-balkan.com.
Pregled sadržaja
- Šta uzrokuje Inflaciju?
- Da li nam je infacija potrebna?
- Kako se meri inflacija?
- Da li inflacija pokreće ekonomski rast?
- Da li inflacija pokreće ili umanjuje nejednakost bogatstva?
- Gde se danas javlja inflacija?
- Šta je deflacija?
- Kakav uticaj inflacija ima na društvo?
Inflacija može da bude uznemirujuća tema, jer uključuje amorfni koncept novca. Međutim, inflacija je zapravo jednostavna tema koja je napravljena da bude složena razdvajanjem novca i drugih dobara. U ovom članku razlažemo inflaciju i njene uzroke.
Najjednostavnija definicija inflacije je rast cena dobara i usluga. Kada cene rastu, to takođe znači da vrednost jedinice novca – poput dolara – opada. Uzmimo primer McDonald’s hamburgera: 1955. ovaj skromni hamburger se prodavao za samo 15 centi. U 2018. godini se prodavao za 1,09 USD. U 2021. godini prodaje se za 2,49 USD – ogroman rast cene od 1650%.
To znači da je dolar izgubio dosta svoje vrednosti. 1955. godine mogli ste da kupite gotovo 7 hamburgera za novčanicu od jednog dolara. 2021. godine taj dolar vam ne bi kupio ni jedan hamburger. Zašto se čini da cene uvek rastu tokom vremena? I šta možete da učinite povodom toga? Ovaj članak ima za cilj da odgovori na ta pitanja.
Ekonomisti pokušavaju da sumiraju rast cena mnogih dobara i usluga kao jedan prosečan broj. Ovaj broj predstavlja promenu ukupnih troškova u godišnjim troškovima prosečnog potrošača, kao što su stanarina, hrana i gorivo.
U Sjedinjenim Državama ovaj broj je poznat kao Indeks Potrošačkih Cena, eng. Consumer Price Index (CPI). Kada se CPI poveća tokom određenog vremenskog perioda, ekonomisti kažu da imamo inflaciju. Kada se smanji, to se naziva deflacija.
Šta uzrokuje Inflaciju?
Mnogi izvori kažu da je stalna inflacija koju danas doživljavamo ili uzrokovana povećanjem potražnje (eng. demand-pull) ili smanjenjem ponude usled povećanih proizvodnih troškova (eng. cost-push).
Ovi razlozi nisu tačni – hajde da pogledamo zašto.
Da bismo razumeli pravi razlog inflacije, moramo da sagledamo dve vrste inflacije:
- Inflacija Cena: Cene vremenom rastu.
- Monetarna Inflacija: Količina valute u opticaju raste sa vremenom.
Prva, inflacija cena, retko se javlja tokom dužih perioda (decenije, vekovi) zbog povećane potražnje ili povećanih troškova. Zašto? Tržišta teže da se uravnoteže. Tokom istorije smo više puta videli da povećana potražnja za dobrom povećava njegovu cenu, što podstiče proizvođače da proizvode više tog dobra. Kada se ponuda poveća, cene se smanjuju.
Ovaj ciklus može da potraje nekoliko godina, i javlja se kod gotovo svake robe i „konačnog dobra“ (automobili, televizori, hrana itd.) na Zemlji. Izuzetak su retki metali poput zlata i srebra. Dokazi o tome su prikazani u nastavku.
Kada se poveća trošak za proizvodnju dobra, cena tog dobra često raste da bi pokrila te troškove. Ovaj rast cene dovodi do toga da potrošači tog dobra traže alternativu ili smanjuju potrošnju tog dobra, što dovodi do pada cena na prethodni nivo.
Tržište se prirodno uravnotežava, a cene se smanjuju ili povećanjem ponude ili smanjenjem potražnje.
Da li imamo dokaze da tržišta vremenom uravnotežuju ponudu i potražnju?
Podaci o cenama robe tokom vremena mogu nam dati bolje razumevanje da li tržišta zaista efikasno uravnotežuju ponudu i potražnju. Međutim, cene ne možemo da posmatramo u smislu nacionalnih valuta, jer naše vlade uvek štampaju više svojih nacionalnih valuta.
Oni sprovode monetarnu inflaciju, koja može da izazove inflaciju cena. Posmatranje tržišnih cena u smislu nacionalnih valuta, poput američkog dolara, je poput merenja visine lenjirom koji se neprestano smanjuje. Vaša visina u broju biće sve veća i veća, ali stvarna visina se ne menja.
Mi možemo da znamo da li tržišta uravnotežuju ponudu i potražnju gledajući cene dobara u smislu monetarnog dobra koje ima vrlo konzistentnu ponudu tokom vremena.
Vremenom se pokazalo da zlato ima najmanju monetarnu inflaciju od svih postojećih valuta i dobara. To čini zlato odličnim ‘lenjirom’ za merenje da li tržišta vremenom uravnotežuju ponudu i potražnju. Da bismo bolje razumeli inflaciju cena tokom vremena, pitaćemo koliko unci zlata nešto košta tokom vremena.
Cene u zlatu pokazuju nam da se tržišta vremenom uravnotežuju
Ako cene dobara posmatramo u obliku zlata, vidimo da cene robe prate srednje tačke tokom dužih vremenskih perioda.
Nafta, na primer, je vrlo nestabilna, ali ima tendenciju da se kreće oko 2,5 grama zlata po barelu.
 WTI Sirova Nafta u gramima Zlata po Barelu
WTI Sirova Nafta u gramima Zlata po BareluCena nafte je promenljiva, ali tokom decenija ima tendenciju da se kreće po strani.
Cene kuća tokom proteklih 10 godina takođe su prilično stabilne, iako imamo fiksnu količinu zemlje na planeti. Vidimo da cene kuća u pogledu zlata imaju tendenciju da variraju oko indeksne cene od oko 80, prikazane na grafikonu.
 Shiller-ov US indeks cena kuća u USD i zlatu
Shiller-ov US indeks cena kuća u USD i zlatuOvaj grafikon je na logaritamskoj skali, što nam omogućava da vizualizujemo zapanjujuća povećanja u zelenoj liniji, koja predstavlja domove u dolarima.
Grafički izražene u američkim dolarima, cene ovih dobara uvek rastu – baš kao i McDonald’s hamburger. Da su povećana potražnja ili povećani troškovi odgovorni za konstantnu inflaciju cena, takođe bismo videli kako se cena ove robe povećava u smislu zlata. Podaci iznad pokazuju da su cene konstantne.
Moraju da postoje i drugi razlozi za upornu inflaciju cena koju smo videli u dolarskim iznosima tokom proteklog veka.
Evo šta znamo o tome šta dugoročno utiče na cene, kao u periodu od 1955. do 2018. godine:
- Rast produktivnosti uzrokovan inovacijama, što dovodi do pada cena tokom vremena
- Monetarna inflacija – štampanje velikih količina valute – koja uzrokuje porast cena denominovanih u toj valuti tokom vremena
Znamo da cene izražene u dolarima, eurima i ostalim valutama neprestano rastu. Ako ne mislimo da naša produktivnost kao društva ide unazad, postoji samo jedan jednostavan razlog za inflaciju cena: štampanje većih količina valute, iliti monetarna inflacija.
Naše vlade i banke su zapravo prilično iskrene u pogledu zapanjujućih količina valute koje štampaju. Oni nam svakodnevno govore da oni uzrokuju monetarnu inflaciju.
Da li nam je infacija potrebna?
Bez uporne monetarne inflacije (koja uzrokuje inflaciju cena), naša celokupna savremena ekonomija bi se srušila.

Dozvolite da vam objasnim. Sledeći odeljak može da bude šokantan, i ohrabrujem vas da i sami istražite ukoliko mislite da nisam u pravu.
Kada centralne banke i komercijalne banke daju zajmove, one stvaraju novu valutu.
Kada centralne banke daju zajmove vladama “kupujući državni dug”, one stvaraju novu valutu kada to urade. To omogućava vladama da vode budžetski deficit trošeći više nego što uzimaju od poreza. U tom procesu državni dug se nagomilava.
Komercijalne banke stvaraju novu valutu kada daju zajmove fizičkim licima i preduzećima. Jedino ograničenje koliko novog novca mogu da stvore je zakonski zahtev da banka ima na raspolaganju određeni procenat od ukupnog iznosa novca koji su ljudi deponovali. Zbog toga je naš bankarski sistem poznat kao delimična rezerva – banke pri ruci moraju da imaju samo deo vašeg novca.

Stvaranje valute je neophodno da bi održalo sistem u životu
Budući da se svi zajmovi uglavnom sastoje od novostvorene valute, mora se stvoriti još više valute da bi se taj dug otplatio. A evo i zašto:
Recimo da su prošle godine sve svetske kreditne aktivnosti dovele do stvaranja 100 milijardi dolara. Svih tih 100 milijardi dolara je novostvoreno, i one se duguju bankama sa nekom dodatnom vrednošću za kamate. Odakle dolazi ova dodatna valuta za plaćanje kamata? Budući da ovde govorimo o celokupnoj svetskoj ekonomiji, to plaćanje kamata mora da dodje iz nove količine novostvorene valute.
Sve jedinice današnjih valuta nastale su pozajmljivanjem, a isplata kamate na te zajmove znači da moramo stalno da stvaramo još više nove valute. To dovodi do beskrajne monetarne inflacije. Kada nova valuta cirkuliše kroz ekonomiju, to dovodi do porasta cena: inflacije cena.
 Previše monetarne inflacije može dovesti do hiperinflacije cena. U Venecueli je krajem 2018. godine piletina koštala preko 14 miliona Bolivara. Izvor: NBC News
Previše monetarne inflacije može dovesti do hiperinflacije cena. U Venecueli je krajem 2018. godine piletina koštala preko 14 miliona Bolivara. Izvor: NBC NewsMonetarni sistem se raspada ako se ova monetarna inflacija zaustavi, jer bi to značilo da veliki broj onih koji su uzeli zajam širom sveta ne bi mogao da vrati novac koji su pozajmili – oni ne bi izmirili svoje dugove.
Banke ili zajmodavci koji drže dug tada bi imali bezvrednu imovinu. Budući da vrednost duga podupire vrednost valute, vrednost valute bi strmoglavo padala zajedno sa dugom.
Kada ljudi izgube poverenje u ’tradicionalnu’ valutu, ona brzo postane bezvredna. To se dogodilo u Nemačkoj nakon Prvog svetskog rata, u Peruu devedesetih, Jugoslaviji 1994. ,Zimbabveu, Venecueli i sa još bezbroj drugih tradicionalnih valuta. Da bi odložile ovaj neizbežni ishod dokle god mogu, centralne banke jačaju poverenje u sistem nastavljajući da štampaju valutu stabilnim kursom.
Ovo osigurava da većina ljudi koju su uzeli zajam ima valutu za otplatu svojih kredita. Upravo to se dešava kada vlada izvrši „spas“ kao 2008. ili 2020. – oni osiguravaju da svi imaju dovoljno novca za plaćanje dugova, tako da laž može da se nastavi.
Inflacija ne dolazi iz povećanja potražnje
Sa više valute u opticaju, monetarna inflacija može da izgleda kao povećanje potražnje. Međutim, ekonomisti koji kažu da povećana potražnja pokreće stabilnu inflaciju tokom decenija propuštaju suptilnu poentu: iako monetarna inflacija može da prouzrokuje veću potrošnju, to nije zato što su ljudi zaista bogatiji, već zato što veruju da su bogatiji.
Kada se puno novca ubrizga u ekonomiju, cene jednostavno rastu jer više valute pokriva istu količinu robe. Rast cena znači pad vrednosti valute, tako da nema realnog povećanja stvarnog bogatstva, iako ljudi možda “troše više” u nominalnom iznosu valute.
Uzmimo ovaj primer: vi mesečno zarađujete 1.500 EUR, i prema svom trenutnom načinu života vi mesečno trošite oko 1.500 EUR. Dolazi vlada i počinje da vam daje dodatnih 500 EUR svakog meseca – vi se osećate poprilično dobro, zar ne? Sada možete da izlazite češće u restoran.
Međutim, vlada daje svima po 500 EUR mesečno, i svi ostali takođe troše taj novac. Ekonomista u vladinoj kancelariji, vidi da sada svi troše tih dodatnih 500 EUR mesečno i zaključuje da je vlada ‘stimulisala ekonomiju’.
Ipak, kako sav taj dodatni novac kruži ekonomijom, cene prirodno rastu. Sada vam je potrebno 2.000 EUR da biste održali svoj trenutni način života.
Da li si nešto bogatiji?
Vi možda imate više eura na vašem bankovnom računu, ali svaki od njih vam kupuje manje. Sada trošite 2.000 EUR mesečno da biste živeli životnim stilom koji vas je nekada koštao samo 1.500 EUR mesečno.
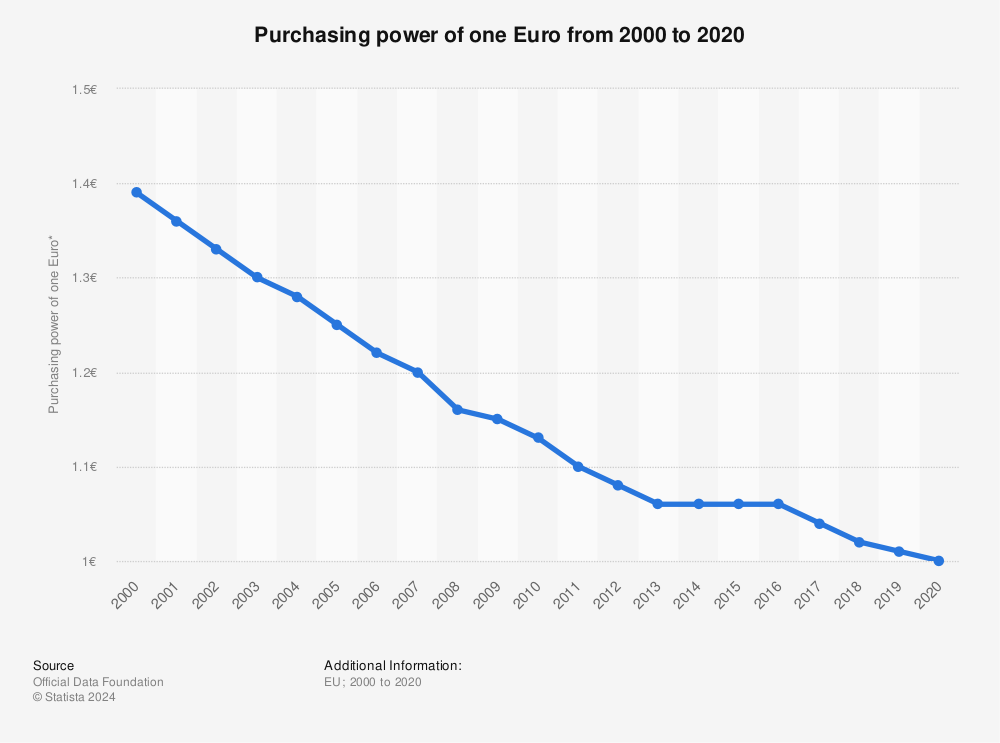
Ovo je ono što monetarna inflacija radi, i zašto je toliko pametnih ekonomista zavarano da misle da povećana potražnja, radije nego štampanje novca, pokreće trajnu inflaciju cena.
Da li smo uvek imali inflaciju?
Stalna inflacija cena relativno je nedavna pojava u modernim ekonomijama i započela je u vreme kada su Sjedinjene Države počele da konstantno štampaju valutu. Ako bi promene ponude i potražnje zaista dugoročno uzrokovale inflaciju cena, videli bismo inflaciju cena tokom istorije. Podaci govore drugačiju priču.
Indeks potrošačkih cena, koji se povećava kada imamo inflaciju cena, bio je prilično konstantan pre početka našeg trenutnog tradicionalnog ’fiat’ monetarnog sistema.
Taj sistem je započeo Bretton Woods-ovim sporazumom iz 1945. godine, a ubrzao se kada je Nixon 1971. okončao svetski zlatni standard.
 Indeks potrošačkih cena, Sjedinjene Države, 1790-2015
Indeks potrošačkih cena, Sjedinjene Države, 1790-2015Kako se meri inflacija?
Inflacija cena se često prikazuje kao promena indeksa potrošačkih cena (CPI). CPI je prosek cena raznih dobara koje ljudi kupuju u svakodnevnom životu: hrane, goriva, stanovanja itd. U Sjedinjenim Državama, vladin odsek pod nazivom Biro za statistiku rada (BLS) meri promene cena. To rade tako što posećuju maloprodajne radnje, beleže cene, računaju prosek i izveštavaju godišnju inflaciju kao promenu u odnosu na prošlu godinu.
Stopa inflacije koja se izveštava, je važna svima jer se koristi za određivanje povećanja troškova života i socijalnih davanja, poput plaćanja socijalnog osiguranja. Kada se CPI prilagodi naniže, isplate zarada i naknada su manje nego što bi trebalo da budu.
Efekti su se vremenom sjedinili: osoba koja u svojoj prvoj godini rada zaradi 40.000 USD zarađivaće samo 52.000 USD u svojoj desetoj godini staža, sa povećanim troškovima života od 3% da bi se plata podudarala sa inflacijom. Ako bi vlada umesto toga prijavila inflaciju od 6%, ta osoba bi u svojoj desetoj godini zarađivala 67.500 USD – tj. oko 30% više. Način na koji izračunavamo i prijavljujemo inflaciju ima ogroman uticaj na zaradu većine zaposlenih i građana.
Ovo je inflacija (procentualna promena u CPI) izmerena u poslednjih 20 godina u Sjedinjenim Državama:
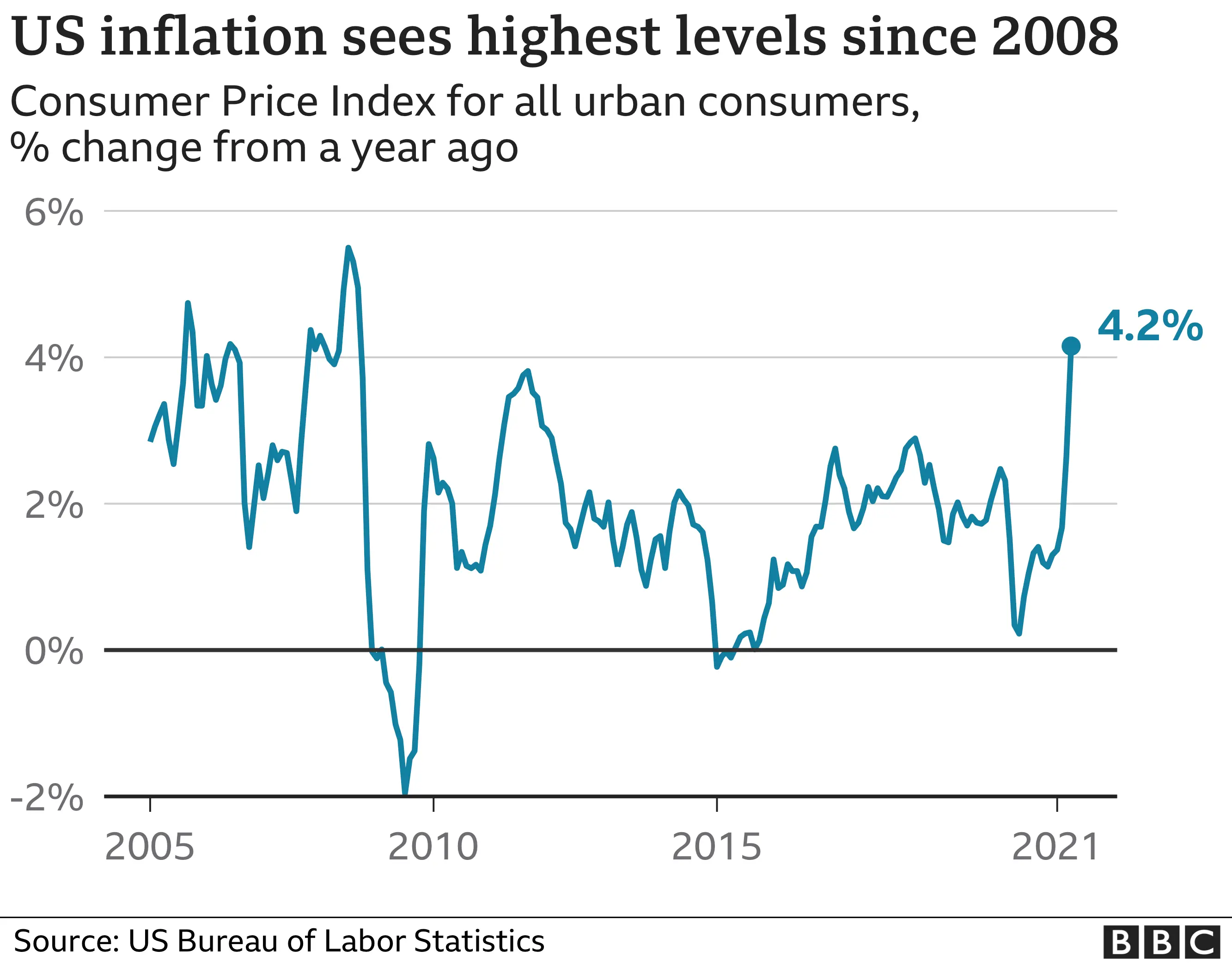
Prvobitno je BLS jednostavno beležio cenu korpe robe široke potrošnje svake godine. Međutim, istraživanje Boskinove Komisije 1996. godine dovelo je do novih alata koji Birou za statistiku rada omogućavaju prilagođavanje cena u CPI. Dva najvažnija alata su geometrijsko ponderisanje i hedonika.
Geometrijsko Ponderisanje
Geometrijsko ponderisanje znači da kupovne navike sada mogu da utiču na to koliko promena cene pojedinog dobra utiče na CPI. Ako potrošači kupe manje robe, ona ima manju težinu kada se ubaci u presek indeksa potrošačkih cena. Boskinova Komisija je tvrdila da bi ova promena pomogla da se promene sklonosti potrošača. Međutim, ne postoji način da se utvrdi da li ljudi menjaju svoje kupovne navike jer zapravo žele da kupuju različite stvari. Vrlo je moguće da ljudi kupuju manje određenog dobra jer ono raste u ceni. Stoga geometrijsko ponderisanje uzrokuje da roba sa velikim rastom cena ima manje uticaja na CPI, što dovodi do niže prijavljene inflacije.
Hedonika
Hedonika omogućava Birou za statistiku rada da menja cenu dobra na osnovu njegovog opaženog povećanja ‘korisnosti’ tokom vremena. Evo primera: recimo da se televizor sa rezolucijom od 720p 2009. godine prodavao za 200 USD. U 2010. godini isti model televizora sada ima rezoluciju od 1080p i prodaje se po istoj ceni: 200 USD. Međutim, pošto se tehnologija u televizoru poboljšala, zaposleni u Birou za statistiku rada mogu da izmisle ‘korisni’ broj i pomoću njega oduzmu deo vrednosti od cene televizora. Kao rezultat, BLS može da kaže da TV košta 180 USD u 2010. godini – iako je njegova cena 200 USD. Ovo dovodi do pada prijavljene inflacije.
Oba ova prilagođavanja smanjuju prijavljenu stopu inflacije, što smanjuje povećanje troškova života i isplate naknada za socijalno osiguranje. Koliko ta prilagođavanja inflacije pogađaju radničku klasu i penzionere? Neke procene, poput procena ekonomiste John Williams-a, sa koledža u Darmouthu, stavljaju stvarnu inflaciju u SAD na u proseku 3% – 6% više nego što je izveštavano od strane Bira za statistiku rada. To bi inflaciju u 2020 dovelo do 5% – 8%, umesto na prijavljenih 2%.
U 2021. godini prijavljena inflacija je 5.4%, u prvom kvartalu.
Da li inflacija pokreće ekonomski rast?
Mnogi ljudi veruju da stabilna inflacija pokreće ekonomski rast podstičući investicije i potrošnju umesto štednje. Međutim, osnovni ekonomski podaci pobijaju ovu uobičajenu tvrdnju.
Ako za primer uzmemo Sjedinjene Države, nacija je imala samo kratke periode inflacije od 1775. do oko 1950. godine, kao što pokazuje indeks potrošačkih cena koji je ostao nepromenjen. Inflacija dobija zamah tek nakon 1971. godine, pa bi bilo za očekivati da će i stopa rasta bruto domaćeg proizvoda (BDP) Sjedinjenih Država porasti nakon 1971. godine.
 Indeks potrošačkih cena, Sjedinjene Države, 1790-2015
Indeks potrošačkih cena, Sjedinjene Države, 1790-2015Međutim, vidimo da se bruto domaći proizvod (BDP) po stanovniku u Sjedinjenim Državama, uobičajena mera ekonomske snage, neprekidno povećavao od 1820. godine do danas po stopi od oko 1,85% godišnje. Ne postoji porast oko 1971. godine, uprkos rastućoj inflaciji koja je započela u to vreme.

Ovo je logaritamski grafikon, koji nam omogućava da bolje vizualizujemo rast tokom vremena: što više logaritamski grafikon podseća na pravu liniju, to je stopa promene konzistentnija. Za više detalja, ovde pogledajte naslov: Rast na tehnološkoj granici i rast dostizanja.
To pokazuje da inflacija ne pokreće ekonomski rast.
Nažalost, imamo dokaze da inflacija ima i druge neželjene posledice, poput nejednakosti bogatstva. Koncentracija bogatstva u top 1%, počela je da raste krajem 1970-ih, nekoliko godina nakon što su Sjedinjene Države skinule svet sa zlatnog standarda i pretvorile se u monetarni sistem zasnovan na dugovima koji zahteva monetarnu inflaciju, a time i inflaciju cena, da bi preživeo.
Za potpunu istoriju tranzicije novca sa robnog sistema na dužni sistem, pročitajte naš članak o novcu.
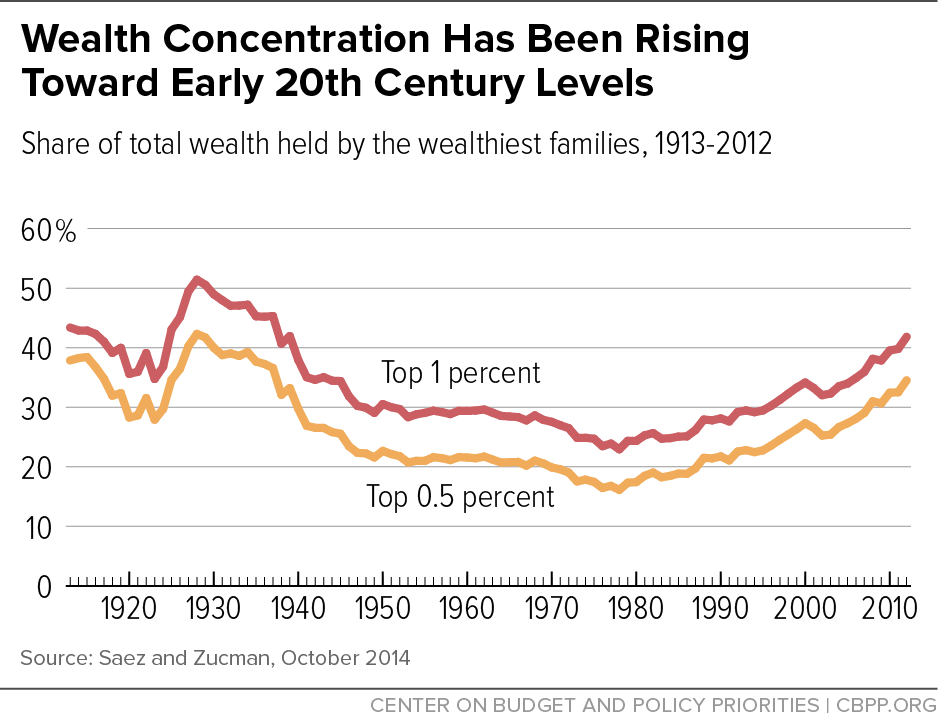
Da li inflacija pokreće ili umanjuje nejednakost bogatstva?
Veza između inflacije i nejednakosti bogatstva postaje jasna kada pogledamo kako novostvorena valuta ulazi u ekonomiju. Vlade, komercijalne banke, velike korporacije i bogati često koriste kredite da bi iskoristili prednosti svojih moći. Kada podignu kredite, oni novonastalu valutu dobijaju ranije od svih ostalih. Oni imaju koristi od inflacije trošenjem nove valute pre nego što cene počnu da rastu kao rezultat te nove valute koja kruži u ekonomiji. Veliki i bogati subjekti često mogu da dobiju kredite po nižim troškovima od prosečnog građanina ili malog preduzeća. To znači da mogu da povećaju svoje poslovanje i bogatstvo brže od manjih firmi.
Bogati mogu da dobiju jeftine zajmove, zahvaljujući Federalnim Rezervama koje zadržavaju niske kamatne stope. To im omogućava da koriste ovo prednost za ostvarivanje ogromne dobiti.
Inflacija pogadja one koji rade za platu i ne mogu da ulože veći deo svog prihoda. Zarade se polako menjaju, ponekad se uskladjuju samo jednom godišnje. Kao rezultat, cene osnovnih dobara i usluga često rastu mnogo pre nego što zarade porastu. Cena potrošačke korpe takođe se smanjuje sa manipulacijama indeksom potrošačkih cena (CPI) koji skriva rast inflacije.
Gde se danas javlja inflacija?
Rekordno visoka inflacija javlja se u zemljama kao što su Venecuela, Zimbabve, Turska, Iran, Kuba, Južna Afrika i Argentina. To dovodi do sloma trgovine i političke nestabilnosti.
U razvijenom svetu vlade izveštavaju o niskoj inflaciji cena. Međutim, globalni bankarski sistem stvara nove valute u tonama – u toku je velika monetarna inflacija. Centralne banke dovode do sve većeg stvaranja valuta snižavanjem kamatnih stopa. To dovodi do toga da korporacije i pojedinci mogu da uzimaju jeftinije kredite, a svaki kredit znači stvaranje nove valute. Od 2008. godine, gotovo sve glavne centralne banke postavile su kamatne stope blizu nule.
Mnoge centralne banke takođe su pozajmljivale ogromne iznose vladama i bankama koje su propale nakon finansijske krize 2008. godine. Za samo nekoliko meseci, ovo je udvostručilo (ponekad utrostručilo ili učetvorostručilo) novčanu masu mnogih nacija. Oni su ovo nazvali „kvantitativno ublažavanje“.
Ako banke koriste toliku monetarnu inflaciju, zašto onda mi ne vidimo inflaciju cena?
Jednostavno rečeno, većina nove valute nije dospela u ruke običnih ljudi. Kada obični ljudi budu mogli da potroše novoštampanu valutu na svoje svakodnevne potrebe, tada ćemo videti rast CPI i inflacije.
Danas većina valuta ulazi u svet putem bankarskih zajmova, pa banke igraju veliku ulogu u tome gde se dešava inflacija. Banke prvenstveno pozajmljuju vrlo ‘sigurnim’ klijentima poput bogatih pojedinaca, vlada i velikih korporacija. Ovi subjekti kupuju luksuznu robu, umetnička dela, finansijsku imovinu i državne obveznice.
Cene ovih vrsta imovine nisu uključene u CPI, tako da je prijavljena inflacija niska. Kao rezultat, povećanje plata i isplate socijalnog osiguranja su takođe na niskom nivou.
 Bogati su uživali u periodu od 2008. do 2021. godine, kada je njihova imovina upumpavana sa velikom količinom novog novca proizvedenog od bankarskih kredita!
Bogati su uživali u periodu od 2008. do 2021. godine, kada je njihova imovina upumpavana sa velikom količinom novog novca proizvedenog od bankarskih kredita!Šta se dešava kada nova valuta dodje u ruke običnih ljudi?
Nažalost, jednog dana će sva ova nova valuta da uđe u normalnu ekonomiju i time će se povećati cene svakodnevne robe. To je poćelo da se dešava 2021. godine kao rezultat stimulativnih programa COVID-19 u Sjedinjenim Državama, koji su ljudima distribuirali trilione dolara. Iako je ovo zasigurno poželjnije od spašavanja korporacija, svaka vrsta spašavanja koja uključuje štampanje novca ima gadne dugoročne efekte.
Ovo što sada doživljavamo dogodilo se u Nemačkoj tokom i posle Prvog svetskog rata. Cene u Nemačkoj su zapravo pale tokom Prvog svetskog rata uprkos velikom stvaranju valute od strane Nemačke centralne banke. Nisko poverenje u ekonomiju sprečavalo je nemački narod da troši novac. Međutim, kad se rat završio i kada su ljudi ponovo počeli da ga troše, cene su vrlo naglo skočile i valuta je postala bezvredna. To bi moglo da se dogodi 2020-ih u Sjedinjenim Državama, sa obzirom na predložene programe podsticaja.
Politike poput Univerzalnog Osnovnog Dohotka, eng. Universal Basic Income (UBI), koje izgledaju pogodne za njihova obećanja da će “spasiti ljude”, takođe mogu da pokrenu hiperinflaciju. Obični ljudi bi se osećali imućnije, trošili bi svoju novoštampanu valutu i doveli do brzog rasta cena. Ovo bi u suštini poništilo pozitivan uticaj građana koji dobijaju “besplatan novac” svakog meseca.
Pa kako onda vi možete da zaštitite svoju ušteđevinu od inflacije? Kupujte imovinu koja je retka, potcenjena i koju vlade teško mogu da prigrabe. Ova imovina su plemeniti metali poput zlata, i Bitcoin.
Šta je deflacija?
Deflacija znači pad cena tokom vremena. Mnogi ekonomisti kažu da će ovo dovesti do toga da ljudi gomilaju valutu i da će dovesti do ekonomskog kolapsa, jer ljudi prestaju da kupuju robu i ulažu u preduzeća. To jednostavno nije tačno, jer ljudi uvek imaju potrebe i želje zbog kojih kupuju odredjenu robu. Stalni pad cena tokom vremena jednostavno bi promenio psihologiju potrošačke kulture u kojoj živimo.
Potrošačka kultura potiče od inflacije
Kako je to istina? Pogledajmo na sledećem primeru. Recimo da želite novi auto i da imate dovoljno novca da ga kupite. Poznato je da u našem svetu zbog stalne inflacije vaš novac vremenom postaje sve manje i manje vredan. U paralelnom svemiru u kojem se javlja stalna deflacija, vaš novac vremenom postaje sve vredniji.
- Uz konstantnu inflaciju, auto će koštati nešto više sledeće godine, i nešto više naredne godine. Niste sigurni gde da uložite novac da biste sa vremenom sigurno očuvali njegovu kupovnu moć. Ako niste sigurni da li ćete da kupite auto, ima više finansijskog smisla da ga kupite odmah, da biste dobili najbolju ponudu.
- Uz konstantnu deflaciju, auto će koštati nešto manje sledeće, i još manje naredne godine. Ako samo čuvate vaš novac, sledeće godine ćete dobiti bolju ponudu za auto. Ako niste sigurni da li ćete da kupite auto, ima više finansijskog smisla da sačekate malo duže da biste dobili bolju ponudu.
Sada razmislite o ta dva scenarija, pomnožena bilionima ljudi i proizvoda. Uz konstantnu inflaciju, svako ima malo više razloga da kupuje stvari upravo sada. Uz konstantnu deflaciju, svi sada imaju malo manje razloga da kupuju. Upravo na taj način inflacija je u osnovi naše materijalističke, potrošačke kulture. Deflacija bi mogla da bude lek.
Inflacija uzrokuje loše investicije
Vaš novac godišnje gubi “2%” svoje vrednosti zbog inflacije. Sada, recimo da vas Stefan pita da investirate u njegov Fast food. Nakon uvida u brojeve, verujete da ćete ovom investicijom izgubiti 1% od vrednosti svog novca. Gubitak od 1% u Stefanovom poslu bolji je od gubitka od 2% zbog inflacije, pa se vi odlučujete da uložite. Ovo je loša investicija, eng. malinvestment – investirajući vi ćete da izgubite deo vrednosti. Međutim, čuvanje valute je još gore, zato ulažete.
Mnogi investitori, poput penzijskih fondova, danas su prisiljeni da investiraju u neprofitabilne biznise zbog investicionih mandata i same veličine njihove ‘imovine pod upravljanjem’.
Pristalice konstantno niske inflacije veruju da bi deflacija smanjila investicije. Međutim, to bi samo smanjilo ulaganje u preduzeća sa negativnim očekivanim prinosom poput Stefanovog Fast food-a. Na primer, recimo da je deflacija u proseku oko 2% godišnje. Na ovom tržištu investitori bi jednostavno prestali da ulažu u projekte za koje misle da će im zaraditi manje od 2% godišnjeg povrata ulaganja.
Neznatno deflaciona valuta obeshrabriće ulaganja u lažna i loša preduzeća i podstaći ulaganje u solidna preduzeća koja svetu dodaju vrednost.
Kakav uticaj inflacija ima na društvo?
Inflacija pokreće povećanu potrošnju, smanjenu štednju i povećani dug. Sve ove stvari dovode do toga da većina ljudi mora da radi više sati i duže u starosti. Iako inflacija kažnjava one koji rade za platu, ona obogaćuje vlasnike bilo koje imovine koja dobija na ceni kada nova valuta uđe u sistem. Ova imovina uključuje akcije, umetnička dela, nekretnine i drugu imovinu koju bogataši koriste za čuvanje svog bogatstva.
Vremenom ljudi i firme izmišljaju nove načine za jeftinije stvaranje dobara i usluga višeg kvaliteta. Ovo je poznato kao ‘rast produktivnosti’ i trebalo bi da uzrokuje da cene tokom vremena konstantno padaju, a ne da rastu. Samo konstantno stvaranje valute koje je neophodno zbog monetarnog sistema zasnovanog na dugu naše vlade uzrokuje stalnu inflaciju i njene loše efekte.
Ako vam se sviđa moj rad, molim vas da ga podelite sa svojim prijateljima i porodicom. Cilj mi je da svima pružim pogled u ekonomiju i na to kako ona utiče na njihov život.
-
 @ 58537364:705b4b85
2025-05-24 20:48:43
@ 58537364:705b4b85
2025-05-24 20:48:43“Any society that sets intellectual development as its goal will continually progress, without end—until life is liberated from problems and suffering. All problems can ultimately be solved through wisdom itself.
The signpost pointing toward ‘wisdom’ is the ability to think—or what is called in Dhamma terms, ‘yoniso-manasikāra,’ meaning wise or analytical reflection. Thinking is the bridge that connects information and knowledge with insight and understanding. Refined or skillful thinking enables one to seek knowledge and apply it effectively.
The key types of thinking are:
- Thinking to acquire knowledge
- Thinking to apply knowledge effectively In other words, thinking to gain knowledge and thinking to use that knowledge. A person with knowledge who doesn’t know how to think cannot make that knowledge useful. On the other hand, a person who thinks without having or seeking knowledge will end up with nothing but dreamy, deluded ideas. When such dreamy ideas are expressed as opinions, they become nonsensical and meaningless—mere expressions of personal likes or dislikes.
In this light, the ‘process of developing wisdom’ begins with the desire to seek knowledge, followed by the training of thinking skills, and concludes with the ability to express well-founded opinions. (In many important cases, practice, testing, or experimentation is needed to confirm understanding.)
Thus, the thirst for knowledge and the ability to seek knowledge are the forerunners of intellectual development. In any society where people lack a love for knowledge and are not inclined to search for it, true intellectual growth will be difficult. That society will be filled with fanciful, delusional thinking and opinions based merely on personal likes and dislikes. For the development of wisdom, there must be the guiding principle that: ‘Giving opinions must go hand-in-hand with seeking knowledge. And once knowledge is gained, thinking must be refined and skillful.’”
— Somdet Phra Buddhaghosacariya (P.A. Payutto) Source: Dhamma treatise “Organizing Society According to the Ideals of the Sangha”
Note: “Pariyosāna” means the complete conclusion or the final, all-encompassing end.
“We must emphasize the pursuit of knowledge more than merely giving opinions. Opinions must be based on the most solid foundation of knowledge.
Nowadays, we face so many problems because people love to express opinions without ever seeking knowledge.”
— Somdet Phra Buddhaghosacariya (P.A. Payutto)