-
 @ 21335073:a244b1ad
2025-05-09 13:56:57
@ 21335073:a244b1ad
2025-05-09 13:56:57Someone asked for my thoughts, so I’ll share them thoughtfully. I’m not here to dictate how to promote Nostr—I’m still learning about it myself. While I’m not new to Nostr, freedom tech is a newer space for me. I’m skilled at advocating for topics I deeply understand, but freedom tech isn’t my expertise, so take my words with a grain of salt. Nothing I say is set in stone.
Those who need Nostr the most are the ones most vulnerable to censorship on other platforms right now. Reaching them requires real-time awareness of global issues and the dynamic relationships between governments and tech providers, which can shift suddenly. Effective Nostr promoters must grasp this and adapt quickly.
The best messengers are people from or closely tied to these at-risk regions—those who truly understand the local political and cultural dynamics. They can connect with those in need when tensions rise. Ideal promoters are rational, trustworthy, passionate about Nostr, but above all, dedicated to amplifying people’s voices when it matters most.
Forget influencers, corporate-backed figures, or traditional online PR—it comes off as inauthentic, corny, desperate and forced. Nostr’s promotion should be grassroots and organic, driven by a few passionate individuals who believe in Nostr and the communities they serve.
The idea that “people won’t join Nostr due to lack of reach” is nonsense. Everyone knows X’s “reach” is mostly with bots. If humans want real conversations, Nostr is the place. X is great for propaganda, but Nostr is for the authentic voices of the people.
Those spreading Nostr must be so passionate they’re willing to onboard others, which is time-consuming but rewarding for the right person. They’ll need to make Nostr and onboarding a core part of who they are. I see no issue with that level of dedication. I’ve been known to get that way myself at times. It’s fun for some folks.
With love, I suggest not adding Bitcoin promotion with Nostr outreach. Zaps already integrate that element naturally. (Still promote within the Bitcoin ecosystem, but this is about reaching vulnerable voices who needed Nostr yesterday.)
To promote Nostr, forget conventional strategies. “Influencers” aren’t the answer. “Influencers” are not the future. A trusted local community member has real influence—reach them. Connect with people seeking Nostr’s benefits but lacking the technical language to express it. This means some in the Nostr community might need to step outside of the Bitcoin bubble, which is uncomfortable but necessary. Thank you in advance to those who are willing to do that.
I don’t know who is paid to promote Nostr, if anyone. This piece isn’t shade. But it’s exhausting to see innocent voices globally silenced on corporate platforms like X while Nostr exists. Last night, I wondered: how many more voices must be censored before the Nostr community gets uncomfortable and thinks creatively to reach the vulnerable?
A warning: the global need for censorship-resistant social media is undeniable. If Nostr doesn’t make itself known, something else will fill that void. Let’s start this conversation.
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ c11cf5f8:4928464d
2024-09-01 13:22:49
@ c11cf5f8:4928464d
2024-09-01 13:22:49Let's hear some of your latest Bitcoin purchases, feel free to include links to the shops or merchants you bought from too!
If you missed our last thread, here are some of the items stackers recently spent their sats on.
originally posted at https://stacker.news/items/668607
-
 @ 8f69ac99:4f92f5fd
2025-05-16 11:40:35
@ 8f69ac99:4f92f5fd
2025-05-16 11:40:35Há algo quase reconfortante na previsibilidade com que certos colunistas abordam Bitcoin: a cada oportunidade, repetem os mesmos chavões, reciclados com indignação moralista e embrulhados numa embalagem de falsa autoridade. O artigo publicado na Visão, com o título dramático "De criança prodígio a adolescente problemático", encaixa-se perfeitamente nesse molde.
Trata-se de uma peça de opinião que mistura factos irrelevantes com interpretações enviesadas, estatísticas sem contexto e um medo mal disfarçado de perder o monopólio da narrativa económica. A autora, Sofia Santos Machado, opta por colar em Bitcoin os desastres do chamado “mundo cripto” como se fossem parte do mesmo fenómeno — ignorando, por conveniência ou ignorância, que Bitcoin não é altcoins, não é NFTs, não é esquemas de yield exótico, e não é fintech vestida de blockchain.
Esta resposta centra-se exclusivamente em Bitcoin — um protocolo monetário aberto, incorruptível e resistente à censura, que já está a servir como salvaguarda de valor em regiões onde o sistema financeiro convencional falhou. Não me interessa defender pirâmides, tokens inflacionários ou aventuras bancárias mal calculadas.
Criticar Bitcoin é legítimo — mas fazê-lo sem saber do que se fala é apenas desinformação.
A Histeria da Água — Falar Sem Saber
O artigo abre com uma pérola alarmista sobre o consumo de água:
“Uma única transacção de bitcoin consome seis milhões de vezes mais água do que um pagamento com cartão.”
Seis. Milhões. De vezes. Resta saber se a autora escreveu isto com cara séria ou a rir-se enquanto bebia água engarrafada dos Alpes Suíços.
Fontes? Metodologia? Contexto? Estou a brincar — isto é a Visão, onde os números são decoração e os factos opcionais.
Claro que comparar transacções na camada base de Bitcoin com pagamentos "instantâneos" da rede Visa é tão rigoroso como comparar um Boeing 747 com um avião de papel porque um voa mais longe. Um artigo sério teria falado em batching, na Lightning Network, ou no facto de que Bitcoin nem sequer compete com a Visa nesse nível, nem em nenhum. Mas isso exigiria, imagine-se, investigação.
Pior ainda, não há qualquer menção ao consumo de água na extracção de ouro, nos data centers bancários, ou no treino de modelos de inteligência artificial. Pelos vistos, só Bitcoin tem de obedecer aos mandamentos ecológicos da Visão. O resto? Santa ignorância selectiva.
Criminosos e o Fantasma do Satoshi
Eis o clássico: “Bitcoin é usado por criminosos”. Um cliché bafiento tirado do baú de 2013, agora reapresentado como se fosse escândalo fresco.
Na realidade, Bitcoin é pseudónimo, não anónimo. Todas as transacções ficam gravadas num livro público — não é propriamente o esconderijo ideal para lavar dinheiro, a menos que sejas fã de disfarces em néon.
E os dados? Claríssimos. Segundo a Chainalysis e a Europol, a actividade ilícita com Bitcoin tem vindo a diminuir. Enquanto isso, os bancos — esses bastiões de confiança — continuam a ser apanhados a lavar biliões para cartéis e cleptocratas. Mas disso a Visão não fala. Devia estragar a narrativa.
O verdadeiro crime aqui é a preguiça intelectual tão profunda que quase merece uma moldura. A Visão tem um editor?
O Espantalho Energético
Como uma criança que acabou de aprender uma palavra nova, a Visão repete “consumo energético” como se fosse um pecado original. Bitcoin usa electricidade — escândalo!
Mas vejamos: o Proof-of-Work não é um defeito. É a razão pela qual Bitcoin é seguro. Não há “desperdício” — há uso, e muitas vezes com energia excedente, renovável, ou que de outro modo seria desperdiçada. É por isso que os mineiros se instalam junto a barragens remotas, queima de gás (flaring), ou parques eólicos no meio do nada — não porque odeiam o planeta, mas porque os incentivos económicos funcionam. Escrevi sobre isso aqui.
O que a Visão convenientemente ignora é que Bitcoin está a ajudar a integrar mais energia renovável nas redes, funcionando como carga flexível. Mas nuance? Trabalho de casa? Esquece lá isso.
Para uma explicação mais séria, podiam ter ouvido o podcast A Seita Bitcoin com o Daniel Batten. Mas para quê investigar?
Cripto = Bitcoin = Fraude?
Aqui chegamos ao buraco negro intelectual: enfiar tudo no mesmo saco. FTX colapsou? Culpa de Bitcoin. Um banqueiro jogou com altcoins? Culpa de Bitcoin. Scam de NFT? Deve ter sido o Satoshi.
Vamos esclarecer: Bitcoin não é “cripto”. Bitcoin é descentralizado, sem líderes, transparente. Não teve pré-mineração, não tem CEO, não promete lucros. O que o rodeia? Tokens centralizados, esquemas Ponzi, pirâmides e vaporware — precisamente o oposto do que Bitcoin representa.
Se um executivo bancário perde o dinheiro dos clientes em Dogecoins, isso é um problema dele. Bitcoin não lhe prometeu nada. Foi a ganância.
E convenhamos: os bancos tradicionais também colapsam. E não precisam de satoshis para isso. Bastam dívidas mal geridas, contabilidade criativa e uma fé cega no sistema.
Culpar Bitcoin por falcatruas “cripto” é como culpar o TCP/IP ou SMTP por emails de phishing. É preguiçoso, desonesto e diz-nos mais sobre a autora do que sobre a tecnologia.
Promessas Por Cumprir? Só Se Não Estiveres a Ver
A "jornalista" da Visão lamenta que “após 15 anos, os riscos são reais mas as promessas por cumprir”. Que promessas? Dinheiro grátis? Cafés pagos com QR codes mágicos?
Bitcoin nunca prometeu fazer cappuccinos mais rápidos. Prometeu soberania monetária, resistência à censura e um sistema previsível. E tem cumprido — diariamente, para milhões. E para o cappuccino, há sempre a Lightning Network.
Pergunta aos venezuelanos, nigerianos, peruanos ou argentinos se Bitcoin falhou. Para muitos, é a única forma de escapar à hiperinflação, ao confisco estatal e à decadência financeira.
Bitcoin não é uma app. É infra-estrutura. É uma nova camada base para o dinheiro global. Não se vê — mas protege, impõe regras e não obedece a caprichos de banqueiros centrais.
E isso assusta. Especialmente quem nunca viveu fora da bolha do euro.
Conclusão: A Visão a Gritar Contra o Progresso
No fim, o artigo da Visão é um festival de clichés, dados errados e ressentimento. Não é só enganador. É desonesto. Culpa a tecnologia pelos erros dos homens. Rejeita o futuro em nome do conforto passado.
Bitcoin não é uma varinha mágica. Mas é a fundação de uma nova liberdade financeira. Uma ferramenta para proteger valor, resistir a abusos e escapar ao controlo constante de quem acha que sabe o que é melhor para ti.
Portanto, fica aqui o desafio, Sofia: se queres criticar Bitcoin, primeiro percebe o que é. Lê o white paper. Estuda. Faz perguntas difíceis.
Caso contrário, és só mais um cão a ladrar para a trovoada — muito barulho, zero impacto.
-
 @ 21335073:a244b1ad
2025-05-21 16:58:36
@ 21335073:a244b1ad
2025-05-21 16:58:36The other day, I had the privilege of sitting down with one of my favorite living artists. Our conversation was so captivating that I felt compelled to share it. I’m leaving his name out for privacy.
Since our last meeting, I’d watched a documentary about his life, one he’d helped create. I told him how much I admired his openness in it. There’s something strange about knowing intimate details of someone’s life when they know so little about yours—it’s almost like I knew him too well for the kind of relationship we have.
He paused, then said quietly, with a shy grin, that watching the documentary made him realize how “odd and eccentric” he is. I laughed and told him he’s probably the sanest person I know. Because he’s lived fully, chasing love, passion, and purpose with hardly any regrets. He’s truly lived.
Today, I turn 44, and I’ll admit I’m a bit eccentric myself. I think I came into the world this way. I’ve made mistakes along the way, but I carry few regrets. Every misstep taught me something. And as I age, I’m not interested in blending in with the world—I’ll probably just lean further into my own brand of “weird.” I want to live life to the brim. The older I get, the more I see that the “normal” folks often seem less grounded than the eccentric artists who dare to live boldly. Life’s too short to just exist, actually live.
I’m not saying to be strange just for the sake of it. But I’ve seen what the crowd celebrates, and I’m not impressed. Forge your own path, even if it feels lonely or unpopular at times.
It’s easy to scroll through the news and feel discouraged. But actually, this is one of the most incredible times to be alive! I wake up every day grateful to be here, now. The future is bursting with possibility—I can feel it.
So, to my fellow weirdos on nostr: stay bold. Keep dreaming, keep pushing, no matter what’s trending. Stay wild enough to believe in a free internet for all. Freedom is radical—hold it tight. Live with the soul of an artist and the grit of a fighter. Thanks for inspiring me and so many others to keep hoping. Thank you all for making the last year of my life so special.
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ 0e29efc2:ff142af2
2025-05-07 15:09:46
@ 0e29efc2:ff142af2
2025-05-07 15:09:46Table of Contents
- Intro
- Important Terminology
- Getting Started
- Where do I buy bitcoin?
- Okay, I bought some bitcoin-now what?
- Less than 0.01 BTC
- More than 0.01 BTC and less than 0.1 BTC
- More than 0.1 BTC
- How Bitcoin Works
- Skepticism
- Someone will hack it
- The government will try to stop it
- It’s not backed by anything
- Conclusion
Intro
Maybe you saw an article in Forbes, a news segment about MicroStrategy (MSTR), or you glanced at the bitcoin price chart; whatever the spark, your curiosity led you here. Enough friends and relatives keep asking me about bitcoin that I finally organized my thoughts into a single reference. This is not a comprehensive guide—it assumes you trust me as a heuristic.
Important Terminology
Sat (satoshi) – the smallest unit of bitcoin. One bitcoin (₿) equals 100 000 000 sats.
Getting Started
Where do I buy bitcoin?
I use River because it publishes proof‑of‑reserves, supports the Lightning Network, and pays interest on idle USD balances (currently 3.8 %).
Okay, I bought some bitcoin-now what?
Withdraw it immediately. Centralized exchanges can and do fail. Your next step depends on how much bitcoin you hold.
If at any point you're struggling, please reach out to me.
Less than 0.01 BTC
- On your phone open Safari (iOS) or Chrome (Android).
- Paste
https://wallet.cashu.me?mint=https://mint.westernbtc.com. Confirm the prompt that asks whether you trusthttps://mint.westernbtc.com. I run this mint so beginners can skip the gnarly parts. - Complete setup.
- Tap Receive → LIGHTNING → enter amount → COPY.
- In River choose Send → Send to a Bitcoin wallet, paste the invoice, verify, and send.
- Return to the wallet; your sats should appear.

More than 0.01 BTC and less than 0.1 BTC
It's time for cold storage. Cold storage means a dedicated signing device not connected to the internet. Think of it like keys to a house. If you have the keys (your cold storage signing device), you can get into your house (the bitcoin). I recommend and use the COLDCARD Q or COLDCARD MK4 from COLDCARD. See this thorough walkthrough.
The creator nostr:npub1rxysxnjkhrmqd3ey73dp9n5y5yvyzcs64acc9g0k2epcpwwyya4spvhnp8 makes reliable content.
More than 0.1 BTC
The next security upgrade involves something called multisig. It requires the use of multiple devices instead of one. Think of those nuclear launch silos in movies where two keys need to be turned in order to launch the missile. One person can't reach both keys, so you need two people. Like the two keys needing to be turned, we need a certain number of keys (signing devices) to be used.

This offers a number of benefits. Say you have a 2-of-3 multisig setup. You would need two of the three keys to move the bitcoin. If you were to lose one, you could use the two others to move it instead. Many choose to geographically distribute the keys; choosing to keep one at a friend’s house or with a bank.
The previous video I linked covers multisig as well. Again, please reach out to me if you need help.
How Bitcoin Works
I'm going to paint a scene portraying the basics of how bitcoin works. Picture a race that's supposed to take 10 minutes to run start-to-finish, and there's a crowd of people spectating. When the fastest runner crosses the finish line, they're awarded 50 bitcoin. Everyone in the crowd recognizes who won, and writes it down on their own scoreboard. Then, the next race begins.
Now, let's say more racers who've had special training join. They start winning consistently because of it, and now the race only lasts about 9 minutes. There's a special rule everyone in the crowd agreed to, that they can make the race harder to ensure it's around 10 minutes long. So they make the race harder to counteract the faster runners.

With this in mind, let's get to the skepticism you might have.
Skepticism
Someone will hack it
Think of bitcoin as the people in the crowd. If someone tries to cheat and writes on their scoreboard that they have a billion bitcoin, their scoreboard is going to look different than everybody else’s. The other people in the crowd will cross-reference with each other and decide to ignore that person who cheated.
The government will try to stop it
Again, think of the crowd. In reality, the "crowd participants" are scattered all around the world. You might be able to stop many of them, but it would be almost impossible to stop everyone. Imagine people are watching the race on TV, can you find everyone who's spectating? Ironically, attempted bans often increase interest.
It’s not backed by anything.
Think of the runners. The runners are bitcoin miners. They have to expend real energy to participate in the race. The more bitcoin miners, the more secure the network. In summary, it's backed by electricity and work.
Conclusion
There are too many topics to cover in one article. I haven't even touched on the history of money, what money is, scarcity, etc. The best way to learn is to research the topics you're interested in for yourself. It took months of deep diving before I was sold on bitcoin, and I had many touch points before that.
Once you see it though, you can't unsee it.
-
 @ 6c2d68ba:846525ec
2024-09-01 13:02:53
@ 6c2d68ba:846525ec
2024-09-01 13:02:53Dear friend,
it seems like you have decided to turn your back on those walled gardens and set sails to enter uncharted territory. A world without walls, an open world, a world of beautiful chaos. At least for today, I don't intend guiding you out of the safe harbour onto the open, endless sea. Today, my only intent is sharing a few thoughts, before you depart.
As a wise man on Madeira once said, it's not so much about having the right answers, it's about asking the right questions. While I'm not certain whether I have found the right questions myself by now, let me share the current set with you:
-
What causes the discomfort that drives you out of the walled garden onto the open sea?
-
Are you trying to transfer from one walled garden to the next one, where the difference being a slightly friendlier colour on the wall?
-
What are you hoping to find on the open sea that walled gardens cannot provide?
-
What are you willing to sacrifice for freedom (of speech)?
-
What will you need to keep the ship afloat?
-
How will you react when you find yourself in the middle of a storm?
I sincerely believe that it's worthwile taking a step back before departing to reflect on the big picture and the underlying paradigm shift between walled gardens and nostr. This is not about building competitors to broken systems, this is not about mimicking centralised services, this is not about repeating the same mistakes over and over.
This is about building a new world, an open world without walled gardens and data silos.
Onwards!
-
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 30ceb64e:7f08bdf5
2024-08-14 11:51:36
@ 30ceb64e:7f08bdf5
2024-08-14 11:51:36Heres a scenario:
Imagine you have a nostr e-cash/Lightning Wallet and you would like to have a maximum receive balance of 20k split in between 5 mints that enable multipath payments.
Pick 5 mints below to store 4k sats each, the funds are automatically withdrawn to your lightning node at the end of the day.
Stacker News Robosats Sparrow Coinkite Start9 Rabbit Hole Recap @siggy47 Damus LND Your own mint
originally posted at https://stacker.news/items/648298
-
 @ 51bbb15e:b77a2290
2025-05-21 00:24:36
@ 51bbb15e:b77a2290
2025-05-21 00:24:36Yeah, I’m sure everything in the file is legit. 👍 Let’s review the guard witness testimony…Oh wait, they weren’t at their posts despite 24/7 survellience instructions after another Epstein “suicide” attempt two weeks earlier. Well, at least the video of the suicide is in the file? Oh wait, a techical glitch. Damn those coincidences!
At this point, the Trump administration has zero credibility with me on anything related to the Epstein case and his clients. I still suspect the administration is using the Epstein files as leverage to keep a lot of RINOs in line, whereas they’d be sabotaging his agenda at every turn otherwise. However, I just don’t believe in ends-justify-the-means thinking. It’s led almost all of DC to toss out every bit of the values they might once have had.
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ 30ceb64e:7f08bdf5
2024-08-14 11:15:27
@ 30ceb64e:7f08bdf5
2024-08-14 11:15:27It's wild. I just proved I can build #nostr 'wallet' where I can store the encrypted tokens in a Germany relay and make the lightning payment out of a Singapore mint. All using a #nsec that never leaves my machine. https://primal.net/e/note15l02rf4r474ck04mlrxxfagyl0z6t04ltsugf9dtph4xxhzfnd4sqpk74n
I’ve proven to myself that a #nostr wallet can exist across time and space, independently of any one app, server or custodian. The only thing which controls the ‘wallet’ is the generation and control of an #nsec which is free to exist within or flee any jurisdiction.
In my mind, this lays to rest the notion that a wallet needs to be an app, service, or anything that can be captured commercially or by the state. https://primal.net/e/note13nwsh852x9tfex2jade6vwymhhct8zussxr4zwy7uag24hjc9stq0xsxaf
https://image.nostr.build/07dd1b56d6bb60b13cfe6c19d9384bc3ef198d01af4be9a5c544f791b80b746a.png
I am thinking about coining the term “nsac” to refer to a wallet-like thing that can exist on #nostr holding your valuable things, such as ecash tokens. I have already implemented a prototype #cashu ecash wallet which looks to be promising.
So you would have:
npub - your identity
nsec - your private key
nsac - your valuables
Your #nsac could be the same as your #nsec but better case is to generate as many #nsacs as required.
Happy to hear feedback!
For reference, what a ‘sac’ is in the biological sense:
A sac is a biological term referring to a pouch or cavity in an organism that is typically enclosed and may contain fluid, air, or other substances. Sacs can serve various functions depending on their location and role in the body, such as protecting a developing embryo, facilitating the exchange of gases in the lungs, or reducing friction between moving parts in joints
https://primal.net/e/note1snj7y9m6f7lhfzkd2ujzqcvparpgddzmgcgwsgghqvkcyd0rkqhsmmlyla
npub1q6mcr8tlr3l4gus3sfnw6772s7zae6hqncmw5wj27ejud5wcxf7q0nx7d5
Wild stuff freaks, will nostr become the best lightning/E-Cash wallet? Let me know what you think.
originally posted at https://stacker.news/items/648270
-
 @ 8f69ac99:4f92f5fd
2025-05-06 14:21:13
@ 8f69ac99:4f92f5fd
2025-05-06 14:21:13A concepção popular de "anarquia" evoca frequentemente caos, colapso e violência. Mas e se anarquia significasse outra coisa? E se representasse um mundo onde as pessoas cooperam e se coordenam sem autoridades impostas? E se implicasse liberdade, ordem voluntária e resiliência—sem coerção?
Bitcoin é um dos raros exemplos funcionais de princípios anarquistas em acção. Não tem CEO, nem Estado, nem planeador central—e, no entanto, o sistema funciona. Faz cumprir regras. Propõe um novo modelo de governação e oferece uma exploração concreta do anarcocapitalismo.
Para o compreendermos, temos de mudar de perspectiva. Bitcoin não é apenas software ou um instrumento de investimento—é um sistema vivo: uma ordem espontânea.
Ordem Espontânea, Teoria dos Jogos e o Papel dos Incentivos Económicos
Na política e economia contemporâneas, presume-se geralmente que a ordem tem de vir de cima. Governos, corporações e burocracias são vistos como essenciais para organizar a sociedade em grande escala.
Mas esta crença nem sempre se verifica.
Os mercados surgem espontaneamente da troca. A linguagem evolui sem supervisão central. Projectos de código aberto prosperam graças a contribuições voluntárias. Nenhum destes sistemas precisa de um rei—e, no entanto, têm estrutura e funcionam.
Bitcoin insere-se nesta tradição de ordens emergentes. Não é ditado por uma entidade única, mas é governado através de código, consenso dos utilizadores e incentivos económicos que recompensam a cooperação e penalizam a desonestidade.
Código Como Constituição
Bitcoin funciona com base num conjunto de regras de software transparentes e verificáveis. Estas regras determinam quem pode adicionar blocos, com que frequência, o que constitui uma transacção válida e como são criadas novas moedas.
Estas regras não são impostas por exércitos nem pela polícia. São mantidas por uma rede descentralizada de milhares de nós, cada um a correr voluntariamente software que valida o cumprimento das regras. Se alguém tentar quebrá-las, o resto da rede simplesmente rejeita a sua versão.
Isto não é governo por maioria—é aceitação baseada em regras.
Cada operador de nó escolhe qual versão do software quer executar. Se uma alteração proposta não tiver consenso suficiente, não se propaga. Foi assim que as "guerras do tamanho do bloco" foram resolvidas—não por votação, mas através de sinalização do que os utilizadores estavam dispostos a aceitar.
Este modelo de governação ascendente é voluntário, sem permissões, e extraordinariamente resiliente. Representa um novo paradigma de sistemas autorregulados.
Mineiros, Incentivos e a Segurança Baseada na Teoria dos Jogos
Bitcoin assegura a sua rede utilizando a Teoria de Jogos. Os mineiros que seguem o protocolo são recompensados financeiramente. Quem tenta enganar—como reescrever blocos ou gastar duas vezes—sofre perdas financeiras e desperdiça recursos.
Agir honestamente é mais lucrativo.
A genialidade de Bitcoin está em alinhar incentivos egoístas com o bem comum. Elimina a necessidade de confiar em administradores ou esperar benevolência. Em vez disso, torna a fraude economicamente irracional.
Isto substitui o modelo tradicional de "confiar nos líderes" por um mais robusto: construir sistemas onde o mau comportamento é desencorajado por design.
Isto é segurança anarquista—não a ausência de regras, mas a ausência de governantes.
Associação Voluntária e Confiança Construída em Consenso
Qualquer pessoa pode usar Bitcoin. Não há controlo de identidade, nem licenças, nem processo de aprovação. Basta descarregar o software e começar a transaccionar.
Ainda assim, Bitcoin não é um caos desorganizado. Os utilizadores seguem regras rigorosas do protocolo. Porquê? Porque é o consenso que dá valor às "moedas". Sem ele, a rede fragmenta-se e falha.
É aqui que Bitcoin desafia as ideias convencionais sobre anarquia. Mostra que sistemas voluntários podem gerar estabilidade—não porque as pessoas são altruístas, mas porque os incentivos bem desenhados tornam a cooperação a escolha racional.
Bitcoin é sem confiança (trustless), mas promove confiança.
Uma Prova de Conceito Viva
Muitos acreditam que, sem controlo central, a sociedade entraria em colapso. Bitcoin prova que isso não é necessariamente verdade.
É uma rede monetária global, sem permissões, capaz de fazer cumprir direitos de propriedade, coordenar recursos e resistir à censura—sem uma autoridade central. Baseia-se apenas em regras, incentivos e participação voluntária.
Bitcoin não é um sistema perfeito. É um projecto dinâmico, em constante evolução. Mas isso faz parte do que o torna tão relevante: é real, está a funcionar e continua a melhorar.
Conclusão
A anarquia não tem de significar caos. Pode significar cooperação sem coerção. Bitcoin prova isso.
Procuramos, desesperados, por alternativas às instituições falhadas, inchadas e corruptas. Bitcoin oferece mais do que dinheiro digital. É uma prova viva de que podemos construir sociedades descentralizadas, eficientes e justas.
E isso, por si só, já é revolucionário.
Photo by Floris Van Cauwelaert on Unsplash
-
 @ c9badfea:610f861a
2025-05-20 19:49:20
@ c9badfea:610f861a
2025-05-20 19:49:20- Install Sky Map (it's free and open source)
- Launch the app and tap Accept, then tap OK
- When asked to access the device's location, tap While Using The App
- Tap somewhere on the screen to activate the menu, then tap ⁝ and select Settings
- Disable Send Usage Statistics
- Return to the main screen and enjoy stargazing!
ℹ️ Use the 🔍 icon in the upper toolbar to search for a specific celestial body, or tap the 👁️ icon to activate night mode
-
 @ 04c915da:3dfbecc9
2025-05-20 15:53:48
@ 04c915da:3dfbecc9
2025-05-20 15:53:48This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ 04c915da:3dfbecc9
2025-05-20 15:47:16
@ 04c915da:3dfbecc9
2025-05-20 15:47:16Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 6ad3e2a3:c90b7740
2025-05-20 13:49:50
@ 6ad3e2a3:c90b7740
2025-05-20 13:49:50I’ve written about MSTR twice already, https://www.chrisliss.com/p/mstr and https://www.chrisliss.com/p/mstr-part-2, but I want to focus on legendary short seller James Chanos’ current trade wherein he buys bitcoin (via ETF) and shorts MSTR, in essence to “be like Mike” Saylor who sells MSTR shares at the market and uses them to add bitcoin to the company’s balance sheet. After all, if it’s good enough for Saylor, why shouldn’t everyone be doing it — shorting a company whose stock price is more than 2x its bitcoin holdings and using the proceeds to buy the bitcoin itself?
Saylor himself has said selling shares at 2x NAV (net asset value) to buy bitcoin is like selling dollars for two dollars each, and Chanos has apparently decided to get in while the getting (market cap more than 2x net asset value) is good. If the price of bitcoin moons, sending MSTR’s shares up, you are more than hedged in that event, too. At least that’s the theory.
The problem with this bet against MSTR’s mNAV, i.e., you are betting MSTR’s market cap will converge 1:1 toward its NAV in the short and medium term is this trade does not exist in a vacuum. Saylor has described how his ATM’s (at the market) sales of shares are accretive in BTC per share because of this very premium they carry. Yes, we’ll dilute your shares of the company, but because we’re getting you 2x the bitcoin per share, you are getting an ever smaller slice of an ever bigger overall pie, and the pie is growing 2x faster than your slice is reducing. (I https://www.chrisliss.com/p/mstr how this works in my first post.)
But for this accretion to continue, there must be a constant supply of “greater fools” to pony up for the infinitely printable shares which contain only half their value in underlying bitcoin. Yes, those shares will continue to accrete more BTC per share, but only if there are more fools willing to make this trade in the future. So will there be a constant supply of such “fools” to keep fueling MSTR’s mNAV multiple indefinitely?
Yes, there will be in my opinion because you have to look at the trade from the prospective fools’ perspective. Those “fools” are not trading bitcoin for MSTR, they are trading their dollars, selling other equities to raise them maybe, but in the end it’s a dollars for shares trade. They are not selling bitcoin for them.
You might object that those same dollars could buy bitcoin instead, so they are surely trading the opportunity cost of buying bitcoin for them, but if only 5-10 percent of the market (or less) is buying bitcoin itself, the bucket in which which those “fools” reside is the entire non-bitcoin-buying equity market. (And this is not considering the even larger debt market which Saylor has yet to tap in earnest.)
So for those 90-95 percent who do not and are not presently planning to own bitcoin itself, is buying MSTR a fool’s errand, so to speak? Not remotely. If MSTR shares are infinitely printable ATM, they are still less so than the dollar and other fiat currencies. And MSTR shares are backed 2:1 by bitcoin itself, while the fiat currencies are backed by absolutely nothing. So if you hold dollars or euros, trading them for MSTR shares is an errand more sage than foolish.
That’s why this trade (buying BTC and shorting MSTR) is so dangerous. Not only are there many people who won’t buy BTC buying MSTR, there are many funds and other investment entities who are only able to buy MSTR.
Do you want to get BTC at 1:1 with the 5-10 percent or MSTR backed 2:1 with the 90-95 percent. This is a bit like medical tests that have a 95 percent accuracy rate for an asymptomatic disease that only one percent of the population has. If someone tests positive, it’s more likely to be a false one than an indication he has the disease*. The accuracy rate, even at 19:1, is subservient to the size of the respective populations.
At some point this will no longer be the case, but so long as the understanding of bitcoin is not widespread, so long as the dollar is still the unit of account, the “greater fools” buying MSTR are still miles ahead of the greatest fools buying neither, and the stock price and mNAV should only increase.
. . .
One other thought: it’s more work to play defense than offense because the person on offense knows where he’s going, and the defender can only react to him once he moves. Similarly, Saylor by virtue of being the issuer of the shares knows when more will come online while Chanos and other short sellers are borrowing them to sell in reaction to Saylor’s strategy. At any given moment, Saylor can pause anytime, choosing to issue convertible debt or preferred shares with which to buy more bitcoin, and the shorts will not be given advance notice.
If the price runs, and there is no ATM that week because Saylor has stopped on a dime, so to speak, the shorts will be left having to scramble to change directions and buy the shares back to cover. Their momentum might be in the wrong direction, though, and like Allen Iverson breaking ankles with a crossover, Saylor might trigger a massive short squeeze, rocketing the share price ever higher. That’s why he actually welcomes Chanos et al trying this copycat strategy — it becomes the fuel for outsized gains.
For that reason, news that Chanos is shorting MSTR has not shaken my conviction, though there are other more pertinent https://www.chrisliss.com/p/mstr-part-2 with MSTR, of which one should be aware. And as always, do your own due diligence before investing in anything.
* To understand this, consider a population of 100,000, with one percent having a disease. That means 1,000 have it, 99,000 do not. If the test is 95 percent accurate, and everyone is tested, 950 of the 1,000 will test positive (true positives), 50 who have it will test negative (false negatives.) Of the positives, 95 percent of 99,000 (94,050) will test negative (true negatives) and five percent (4,950) will test positive (false positives). That means 4,950 out of 5,900 positives (84%) will be false.
-
 @ 02f0a63d:f91bde2c
2024-08-14 11:13:30
@ 02f0a63d:f91bde2c
2024-08-14 11:13:30Usa PGP para enviar mensajes privados por telegram
PGP es una gran herramienta con la que podremos cifrar nuestras conversaciones en cualquier canal de comunicación. En esta publicación te mostraré la forma más rápida y sencilla para poder usar esta herramienta junto con telegram. Te guiaré en unos pasos sencillos para disponer de todo lo necesario para comunicarte con tus contactos de forma privada. Existen muchas formas de hacerlo, a continuación te enseñaré la mas sencilla en mi opinión, no necesitas conocimientos previos ¡¡Los irás adquiriendo practicando ¡¡
Aplicaciones necesarias
F-Droid
Es una store de aplicaciones open source para android, del cual descargaremos las aplicaciones que necesitamos.
Descarga : https://f-droid.org/F-Droid.apk
Nekogram x
Es un cliente de Telegram open source con funciones añadidas entre las que se encuentra la integración de PGP a través de Openkeychain. La descarga e instalación la realizaremos desde F-droid.
https://github.com/NekoX-Dev/NekoX
Openkeychain
Aplicación para android con el estandar OpenPGP . Con Openkeychain se hace muy sencilla La creación de claves PGP y su uso integrado con Nekogram facilita sus uso.
La descarga e instalación la realizaremos desde F-droid.
Guía para comunicarte de forma privada con tu contraparte
Creación de clave con openkeychain
Te pedirá que introduzcas un nombre para identificar la clave y un correo electrónico (puedes poner uno inventado). Haz click en crear clave.
Podrás ver tus claves almacenadas.
Compartir tu clave pública con el receptor
Una vez creada tu clave, ve al chat en Nekogram con quien vas a compartir tu clave pública, haz click en los 3 puntitos de la esquina superior en el chat.
Elige tu clave y se compartirá en el chat de tu contacto.
Importar clave pública de mi contacto
Necesitas la clave pública de tu contacto para poder cifrar la información y que solo el pueda descifrarla con su clave privada. Pídele a tu contacto que te envíe su clave pública (si no sabe comparte esta guía)para que te la envíe al chat de telegram. Haz click sobre el mensaje con la clave pública y pincha en importar clave.
Se abrirá openkeychain y le daremos a importar.
Y aparecerá almacenada junto con tu clave.
Cifrar mensaje con la clave pública de mi contacto
Una vez creada tu clave e importada la clave pública de tu contacto ya tienes todo para poder cifrar y descifrar los mensajes que os enviéis. En Openkeychain abre el menu pinchando en las 3 rayas horizontales en la esquina superior derecha. le das a cifrar/descifrar.
Elige cifrar texto
En cifrar para : la calve de tu contacto.
En firmar con : tu clave
Escribe el texto que quieres cifrar y lo copias o comparte pinchando en los símbolos de arriba.
Pegalo en el chat del contacto
mensaje cifrado, telegram no puede ver el mensaje que contiene.
Descifrar un mensaje en Nekogram
Podremos descifrar un mensaje cuando el emisor lo haya cifrado con nuestra clave pública. Es tan sencillo como pinchar en el mensaje cifrado y darle a descifrar mensaje en la pantalla que sale. Te llevará a Openkeychain.
Se abrira Openkeychain y te mostrará el mensaje descifrado.
Conclusiones:
Hemos visto la manera más fácil para cifrar y descrifrar mensajes con quien quieras, gracias a Openkeychain y la integración de éste en Nekogram X hacen muy fácil mandar mensajes cifrados que solo tú y tu receptor podeis descifrar.
Este sistema se hace necesario usarlo para enviar información que no quiero que un tercero (servidores de telegram) sepa. Como cuando compartimos información personal, o direcciones de bitcoin para no vincularla a tu cuenta de telegram, etc.
Ya no tienes excusa para hacer uso de tu privacidad y revelarla selectivamente a quien desees.
-
 @ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03
@ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ 256a7941:b828ba8d
2024-08-14 03:28:01
@ 256a7941:b828ba8d
2024-08-14 03:28:01Taking calls, texts and FaceTimes. Be direct Be courageous
originally posted at https://stacker.news/items/647955
-
 @ 8f69ac99:4f92f5fd
2025-05-02 09:29:41
@ 8f69ac99:4f92f5fd
2025-05-02 09:29:41À medida que Portugal se aproxima das eleições legislativas de 2025, a 18 de Maio, torna-se essencial compreender as diferentes propostas políticas e os programas eleitorais dos partidos para votar de forma informada. Este artigo funciona como um índice para uma série de análises realizadas aos programas dos principais partidos, com foco em temas como liberdades individuais, descentralização e crescimento económico.
A Evolução da Esquerda e da Direita: Um Contexto Histórico e Ideológico
Os termos “esquerda” e “direita” surgiram na Revolução Francesa (1789–1799) para distinguir quem se sentava ao lado do presidente da Assembleia: as forças favoráveis às reformas radicais (à esquerda) e as defensoras da monarquia e da ordem estabelecida (à direita). Com o século XIX e o advento do liberalismo económico, a direita passou a associar-se ao livre mercado e ao direito de propriedade, enquanto a esquerda defendeu maior intervenção estatal para promover igualdade.
No final do século XIX e início do século XX, surgiram o socialismo e o comunismo como correntes mais radicais da esquerda, propondo a abolição da propriedade privada dos meios de produção (comunismo) ou sistemas mistos com forte regulação e redistribuição (socialismo). A resposta liberal-conservadora evoluiu para o capitalismo democrático, que combina mercado livre com alguns mecanismos de assistência social.
Hoje, o espectro político vai além do simples eixo esquerda–direita, incluindo dimensões como:
- Autoritarismo vs. Liberdade: grau de controlo do Estado sobre a vida individual e as instituições;
- Intervenção Estatal vs. Livre Mercado: equilíbrio entre regulação económica e iniciativas privadas;
- Igualdade Social vs. Mérito e Responsabilidade Individual: ênfase na redistribuição de recursos ou na criação de incentivos pessoais.
Este modelo multidimensional ajuda a capturar melhor as posições dos partidos contemporâneos e as suas promessas de governação.
Visão Geral das Análises por Partido
Segue-se um resumo dos principais partidos políticos em Portugal, com destaque para a sua orientação ideológica segundo as dimensões de autoritarismo, nível de Intervenção estatal e grau de liberdade individual. Cada nome de partido estará ligado à respectiva análise detalhada.
| Partido | Orientação Ideológica | Nível de Intervenção Estatal | Grau de Liberdade Individual | |----------------------------------------|---------------------------------------------------------------------------------------|------------------------------|------------------------------| | AD – Aliança Democrática (PSD/CDS) | Centro-direita democrática (baixo autoritarismo / equilíbrio intervenção–mercado) | Médio | Médio | | PS – Partido Socialista | Centro-esquerda social-democrata (moderado autoritarismo / intervenção estatal) | Alto | Médio | | CDU – Coligação Democrática Unitária (PCP/PEV) | Esquerda comunista/eco-marxista (mais autoritário / forte intervenção) | Muito alto | Baixo | | IL – Iniciativa Liberal | Liberalismo clássico (muito baixa intervenção / alta liberdade) | Baixo | Muito alto | | Chega | Nacionalismo autoritário (controlo social elevado / mercado regulado com foco interno)| Médio | Baixo | | Livre | Esquerda progressista verde (baixa hierarquia / intervenção social) | Alto | Médio | | BE – Bloco de Esquerda | Esquerda democrática radical (moderado autoritarismo / intervenção forte) | Alto | Médio | | PAN – Pessoas-Animais-Natureza | Ambientalismo progressista (intervenção pragmática / foco em direitos e sustentabilidade) | Médio | Alto | | Ergue-te | Nacionalismo soberanista (autoritarismo elevado / intervenção seletiva com foco nacional) | Médio | Baixo | | ADN – Alternativa Democrática Nacional | Nacionalismo conservador (autoritarismo elevado / intervenção seletiva com foco nacional) | Médio | Baixo |
Análises Detalhadas dos Programas Eleitorais
Estas análises pretendem oferecer aos eleitores uma visão clara e objetiva das propostas de cada partido, facilitando decisões conscientes nas urnas. Ao focar-se nas promessas relacionadas com liberdades individuais, descentralização e crescimento económico, este conjunto de textos ajuda a compreender melhor o impacto potencial de cada escolha política.
Aliança Democrática (AD)
Partido Socialista (PS)
Coligação Democrática Unitária (CDU)
Iniciativa Liberal (IL)
Chega
Livre
Bloco de Esquerda (BE)
Pessoas,Animais e Natureza (PAN)
Alternativa Democrática Nacional (ADN)
Ergue-te
Photo by Brett Kunsch on Unsplash
-
 @ 502ab02a:a2860397
2025-05-24 01:14:43
@ 502ab02a:a2860397
2025-05-24 01:14:43ในสายตาคนรักสุขภาพทั่วโลก “อโวคาโด” คือผลไม้ในฝัน มันมีไขมันดี มีไฟเบอร์สูง ช่วยลดคอเลสเตอรอลได้ มีวิตามินอี มีโพแทสเซียม และที่สำคัญคือ "ดูดี" ทุกครั้งที่ถูกปาดวางบนขนมปังโฮลวีตในชามสลัด หรือบนโฆษณาอาหารคลีนสุดหรู
แต่ในสายตาชาวไร่บางคนในเม็กซิโกหรือชุมชนพื้นเมืองในโดมินิกัน อโวคาโดไม่ใช่ผลไม้แห่งสุขภาพ แต่มันคือสัญลักษณ์ของความรุนแรง การกดขี่ และการสูญเสียเสรีภาพในผืนดินของตัวเอง
เมื่ออาหารกลายเป็นทองคำ กลุ่มอิทธิพลก็ไม่เคยพลาดจะเข้าครอบครอง
เรามักได้ยินคำว่า "ทองคำเขียว" หรือ Green Gold ใช้เรียกอโวคาโด เพราะในรอบ 20 ปีที่ผ่านมา ความต้องการบริโภคของมันพุ่งสูงขึ้นเป็นเท่าตัว โดยเฉพาะในสหรัฐฯ และยุโรป จากผลการวิจัยของมหาวิทยาลัยฮาร์วาร์ดและข้อมูลการส่งออกของ USDA พบว่า 90% ของอโวคาโดที่บริโภคในอเมริกา มาจากรัฐมิโชอากังของเม็กซิโก พื้นที่ซึ่งควบคุมโดยกลุ่มค้ายาเสพติดไม่ต่างจากเจ้าของสวนตัวจริง
พวกเขาเรียกเก็บ “ค่าคุ้มครอง” จากเกษตรกร โดยใช้วิธีเดียวกับมาเฟีย คือ ถ้าไม่จ่าย ก็เจ็บตัวหรือหายตัว ไม่ว่าจะเป็นกลุ่ม CJNG (Jalisco New Generation Cartel), Familia Michoacana หรือ Caballeros Templarios พวกเขาไม่ได้สนใจว่าใครปลูกหรือใครรดน้ำ ตราบใดที่ผลผลิตสามารถเปลี่ยนเป็นเงินได้
องค์กรอาชญากรรมเหล่านี้ไม่ได้แค่ “แฝงตัว” ในอุตสาหกรรม แต่ ยึดครอง ห่วงโซ่การผลิตทั้งหมด ตั้งแต่แปลงปลูกไปจนถึงโรงบรรจุและเส้นทางขนส่ง คนที่ไม่ยอมเข้าระบบมืดอาจต้องพบจุดจบในป่า หรือไม่มีชื่ออยู่ในทะเบียนบ้านอีกต่อไป
จากรายงานของเว็บไซต์ Food is Power องค์กรไม่แสวงกำไรด้านความยุติธรรมด้านอาหารในสหรัฐฯ เผยว่า ในปี 2020 มีเกษตรกรในเม็กซิโกจำนวนมากที่ถูกข่มขู่ บางรายถึงขั้นถูกฆาตกรรม เพราะปฏิเสธจ่ายค่าคุ้มครองจากกลุ่มค้ายา
การปลูกอโวคาโดไม่ใช่เรื่องเบาๆ กับธรรมชาติ เพราะมันต้องการ “น้ำ” มากถึง 272 ลิตรต่อผลเดียว! เรามาดูว่า “272 ลิตร” นี้ เท่ากับอะไรบ้างในชีวิตจริง อาบน้ำฝักบัวนาน 10–12 นาที (โดยเฉลี่ยใช้น้ำ 20–25 ลิตรต่อนาที) ใช้น้ำซักเสื้อผ้าเครื่องหนึ่ง (เครื่องซักผ้า 1 ครั้งกินประมาณ 60–100 ลิตร) น้ำดื่มของคนหนึ่งคนได้นานเกือบ เดือน (คนเราต้องการน้ำดื่มประมาณ 1.5–2 ลิตรต่อวัน)
ถ้าเราใช้ข้อมูลจาก FAO และ Water Footprint Network การผลิตเนื้อวัว 1 กิโลกรัม ต้องใช้น้ำ 15,000 ลิตร (รวมทั้งการปลูกหญ้า อาหารสัตว์ การดื่มน้ำของวัว ฯลฯ) ได้โปรตีนราว 250 กรัม อโวคาโด 1 กิโลกรัม (ราว 5 ผล) ใช้น้ำประมาณ 1,360 ลิตร ได้โปรตีนเพียง 6–8 กรัมเท่านั้น พูดง่ายๆคือ เมื่อเทียบอัตราส่วนเป็นลิตรต่อกรัมโปรตีนแล้วนั้น วัวใช้น้ำ 60 ลิตรต่อกรัมโปรตีน / อโวคาโด ใช้น้ำ 194 ลิตรต่อกรัมโปรตีน แถมการเลี้ยงวัวในระบบธรรมชาติ (เช่น pasture-raised หรือ regenerative farming) ยังสามารถเป็นส่วนหนึ่งของระบบหมุนเวียนน้ำและคาร์บอนได้ พอเห็นภาพแล้วใช่ไหมครับ ดังนั้นเราควรระมัดระวังการเสพสื่อเอาไว้ด้วยว่า คำว่า "ดีต่อโลก" ไม่ได้หมายถึงพืชอย่างเดียว ทุกธุรกิจถ้าทำแบบที่ควรทำ มันยังสามารถผลักดันโลกไม่ให้ตกอยู่ในมือองค์กร future food ได้ เพราะมูลค่ามันสูงมาก
และเมื่อราคาสูง พื้นที่เพาะปลูกก็ขยายอย่างไร้การควบคุม ป่าธรรมชาติในรัฐมิโชอากังถูกแอบโค่นแบบผิดกฎหมายเพื่อแปลงสภาพเป็นไร่ “ทองเขียว” ข้อมูลจาก Reuters พบว่าผลไม้ที่ถูกส่งออกไปยังสหรัฐฯ บางส่วนมาจากแปลงปลูกที่บุกรุกป่าคุ้มครอง และรัฐบาลเองก็ไม่สามารถควบคุมได้เพราะอิทธิพลของกลุ่มทุนและมาเฟีย
ในโดมินิกันก็เช่นกัน มีรายงานจากสำนักข่าว Gestalten ว่าพื้นที่ป่าสงวนหลายพันไร่ถูกเปลี่ยนเป็นไร่อโวคาโด เพื่อป้อนตลาดผู้บริโภคในอเมริกาและยุโรปโดยตรง โดยไม่มีการชดเชยใดๆ แก่ชุมชนท้องถิ่น
สุขภาพที่ดีไม่ควรได้มาจากการทำลายสุขภาพของคนอื่น ไม่ควรมีผลไม้ใดที่ดูดีในจานของเรา แล้วเบื้องหลังเต็มไปด้วยคราบเลือดและน้ำตาของคนปลูก
เฮียไม่ได้จะบอกให้เลิกกินอโวคาโดเลย แต่เฮียอยากให้เรารู้ทัน ว่าความนิยมของอาหารสุขภาพวันนี้ กำลังเป็นสนามใหม่ของกลุ่มทุนโลก ที่พร้อมจะครอบครองด้วย “อำนาจอ่อน” ผ่านแบรนด์อาหารธรรมชาติ ผ่านกฎหมายสิ่งแวดล้อม หรือแม้แต่การครอบงำตลาดเสรีด้วยกำลังอาวุธ
นี่ไม่ใช่เรื่องไกลตัว เพราะเมื่อกลุ่มทุนเริ่มฮุบเมล็ดพันธุ์ คุมเส้นทางขนส่ง คุมฉลาก Certified Organic ทั้งหลาย พวกเขาก็ “ควบคุมสุขภาพ” ของผู้บริโภคเมืองอย่างเราไปด้วยโดยอ้อม
คำถามสำคัญที่มาทุกครั้งเวลามีเนื้อหาอะไรมาฝากคือ แล้วเราจะทำอะไรได้? 555555 - เลือกบริโภคผลไม้จากแหล่งที่โปร่งใสหรือปลูกเองได้ - สนับสนุนเกษตรกรรายย่อยที่ไม่อยู่ภายใต้กลุ่มทุน - ใช้เสียงของผู้บริโภคกดดันให้มีระบบตรวจสอบต้นทางจริง ไม่ใช่แค่ฉลากเขียวสวยๆ - และที่สำคัญ อย่าเชื่อว่า “ทุกสิ่งที่เขาวางให้ดูสุขภาพดี” จะดีจริง (ข้อนี่ละตัวดีเลยครับ)
สุขภาพไม่ใช่สินค้า และอาหารไม่ควรเป็นอาวุธของกลุ่มทุน หากเราเริ่มตระหนักว่าอาหารคือการเมือง น้ำคืออำนาจ และแปลงเกษตรคือสนามรบ เฮียเชื่อว่าผู้บริโภคอย่างเราจะไม่ยอมเป็นหมากอีกต่อไป #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 57c631a3:07529a8e
2025-04-07 13:17:50
@ 57c631a3:07529a8e
2025-04-07 13:17:50What is Growth Engineering? Before we start: if you’ve already filled out the What is your tech stack? survey: thank you! If you’ve not done so, your help will be greatly appreciated. It takes 5-15 minutes to complete. Those filling out will receive results before anyone else, and additional analysis from myself and Elin. Fill out this survey here.**
npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m
Growth engineering was barely known a decade ago, but today, most scaleups and many publicly traded tech companies have dedicated growth teams staffed by growth engineers. However, some software engineers are still suspicious of this new area because of its reputation for hacky code with little to no code coverage.
For this reason and others, I thought it would be interesting to learn more from an expert who can tell us all about the practicalities of this controversial domain. So I turned to Alexey Komissarouk, who’s been in growth engineering since 2016, and was in charge of it at online education platform, MasterClass. These days, Alexey lives in Tokyo, Japan, where he advises on growth engineering and teaches the Growth Engineering course at Reforge.
In today’s deep dive, Alexey covers:
- What is Growth Engineering? In the simplest terms: writing code to help a company make more money. But there are details to consider: like the company size where it makes sense to have a dedicated team do this.
- What do Growth Engineers work on? Business-facing work, empowerment and platform work are the main areas.
- Why Growth Engineers move faster than Product Engineers. Product Engineers ship to build: Growth Engineers ship to learn. Growth Engineers do take shortcuts that would make no sense when building for longevity – doing this on purpose.
- Tech stack. Common programming languages, monitoring and oncall, feature flags and experimentation, product analytics, review apps, and more.
- What makes a good Growth Engineer? Curiosity, “build to learn” mindset and a “Jack of all trades” approach.
- Where do Growth Engineers fit in? Usually part of the engineering department, either operating as with an “owner” or a “hitchiker” model.
- Becoming a Growth Engineer. A great area if you want to eventually become a founder or product manager – but even if not, it can accelerate your career growth. Working in Growth forces you to learn more about the business.
With that, it’s over to Alexey:
I’ll never forget the first time I made my employer a million dollars.
I was running a push notification A/B test for meal delivery startup Sprig, trying to boost repeat orders.
A push notification similar to what we tested to boost repeat orders
Initial results were unpromising; the push notification was not receiving many opens. Still, I wanted to be thorough: before concluding the idea was a failure, I wrote a SQL query to compare order volume for subsequent weeks between customers in test vs control.
The SQL used to figure out the push notification’s efficiency
As it turned out, our test group “beat” the control group by around 10%:
‘review_5_push’ was the new type of push notification. Roughly the same amount of users clicked it, but they placed 10% more in orders
I plugged the numbers into a significance calculator, which showed it was statistically significant – or “stat-sig” – and therefore highly unlikely to be a coincidence. This meant we had a winner on our hands! But how meaningful was it, really, and what would adding the push notification mean for revenue, if rolled out to 100% of users?
It turned out this experiment created an additional $1.5 million dollars, annually, with just one push notification. Wow!
I was hooked. Since that day, I've shipped hundreds of experimental “winners” which generated hundreds of millions of incremental revenue for my employers. But you never forget the first one. Moments like this is what growth engineering is all about.
1. What is Growth Engineering?
Essentially, growth engineering is the writing of code to make a company money. Of course, all code produced by a business on some level serves this purpose, but while Product Engineers focus on creating a Product worth paying for, Growth Engineers instead focus on making that good product have a good business. To this end, they focus on optimizing and refining key parts of the customer journey, such as:
- Getting more people to consider the product
- Converting them into paying customers
- Keeping them as customers for longer, and spending more
What kinds of companies employ Growth Engineers? Places you’ve heard of, like Meta, LinkedIn, DoorDash, Coinbase, and Dropbox, are some of the ones I’ve had students from. There’s also OpenAI, Uber, Tiktok, Tinder, Airbnb, Pinterest… the list of high-profile companies goes on. Most newer public consumer companies you’ve heard have a growth engineering org, too.
Typically, growth engineering orgs are started by companies at Series B stage and beyond, so long as they are selling to either consumers or businesses via SaaS. These are often places trying to grow extremely fast, and have enough software engineers that some can focus purely on growth. Before the Series B stage, a team is unlikely to be ready for growth for various reasons; likely that it hasn’t found product-market fit, or has no available headcount, or lacks the visitor traffic required to run A/B tests.
Cost is a consideration. A fully-loaded growth team consisting of a handful of engineers, a PM, and a designer costs approximately 1 million dollars annually. To justify this, a rule of thumb is to have at least $5 million dollars in recurring revenue – a milestone often achieved at around the Series B stage.
Despite the presence of growth engineering at many public consumer tech companies, the field itself is still quite new, as a discipline and as a proper title.
Brief history of growth engineering
When I joined Opendoor in 2016, there was a head of growth but no dedicated growth engineers, but there were by the time I left in 2020. At MasterClass soon after, there was a growth org and a dozen dedicated growth engineers. So when did growth engineering originate?
The story is that its origins lie at Facebook in 2007. The team was created by then-VP of platform and monetization Chamath Palihapitiya. Reforce founder and CEO Brian Balfour shares:
“Growth (the kind found on an org chart) began at Facebook under the direction of Chamath Palihapitiya. In 2007, he joined the early team in a nebulous role that fell somewhere between Product, Marketing, and Operations. According to his retelling of the story on Recode Decode, after struggling to accomplish anything meaningful in his first year on the job, he was on the verge of being fired.Sheryl Sandberg joined soon after him, and in a hail mary move he pitched her the game-changing idea that led to the creation of the first-ever growth team. This idea not only saved his job, but earned him the lion’s share of the credit for Facebook’s unprecedented growth.At the time, Sheryl and Mark asked him, “What do you call this thing where you help change the product, do some SEO and SEM, and algorithmically do this or that?”His response: “I don’t know, I just call that, like, Growth, you know, we’re going to try to grow. I’ll be the head of growing stuff."And just like that, Growth became a thing.”
Rather than focus on a particular product or feature, the growth team at Facebook focused on moving the needle, and figuring out which features to work on. These days, Meta employs hundreds if not thousands of growth engineers.
2. What do Growth Engineers work on?
Before we jump into concrete examples, let’s identify three primary focus areas that a growth engineer’s work usually involves.
- Business-facing work – improving the business directly
- Empowerment work – enabling other teams to improve the business
- Platform work – improving the velocity of the above activities
Let’s go through all three:
Business-facing work
This is the bread and butter of growth engineering, and follows a common pattern:
- Implement an idea. Try something big or small to try and move a key business metric, which differs by team but is typically related to conversion rate or retention.
- Quantify impact. Usually via A/B testing.
- Analyze impact. Await results, analyze impact, ship or roll back – then go back to the first step.
Experiments can lead to sweeping or barely noticeable changes. A famous “I can’t believe they needed to test this” was when Google figured out which shade of blue generates the most clicks. At MasterClass, we tested things across the spectrum:
- Small: should we show the price right on the homepage, was that a winner? Yes, but we framed it in monthly terms of $15/month, not $180/year.
- Medium: when browsing a course page, should we include related courses, or more details about the course itself? Was it a winner? After lengthy experimentation, it was hard to tell: both are valuable and we needed to strike the right balance.
- Large: when a potential customer is interested, do we take them straight to checkout, or encourage them to learn more? Counterintuitively, adding steps boosted conversion!
Empowerment
One of the best ways an engineer can move a target metric is by removing themselves as a bottleneck, so colleagues from marketing can iterate and optimize freely. To this end, growth engineers can either build internal tools or integrate self-serve MarTech (Marketing Technology) vendors.
With the right tool, there’s a lot that marketers can do without engineering’s involvement:
- Build and iterate on landing pages (Unbounce, Instapage, etc)
- Draft and send email, SMS and Push Notifications (Iterable, Braze, Customer.io, etc)
- Connect new advertising partners (Google Tag Manager, Segment, etc)
We go more into detail about benefits and applications in the MarTech section of Tech Stack, below.
Platform work
As a business scales, dedicated platform teams help improve stability and velocity for the teams they support. Within growth, this often includes initiatives like:
- Experiment Platform. Many parts of running an experiment can be standardized, from filtering the audience, to bucketing users properly, to observing statistical methodology. Historically, companies built reusable Experiment Platforms in-house, but more recently, vendors such as Eppo and Statsig have grown in popularity with fancy statistical methodologies like “Controlled Using Pre-Experiment Data” (CUPED) that give more signal with less data.
- Reusable components. Companies with standard front-end components for things like headlines, buttons, and images, dramatically reduce the time required to spin up a new page. No more "did you want 5 or 6 pixels here" with a designer; instead growth engineers rely on tools like Storybook to standardize and share reusable React components.
- Monitoring. Growth engineering benefits greatly from leveraging monitoring to compensate for reduced code coverage. High-quality business metric monitoring tools can detect bugs before they cause damage.
When I worked at MasterClass, having monitoring at the ad layer prevented at least one six-figure incident. One Friday, a marketer accidentally broadened the audience for a particular ad from US-only, to worldwide. In response, the Facebook Ad algorithm went on a spending spree, bringing in plenty of visitors from places like Brazil and India, whom we knew from past experience were unlikely to purchase the product. Fortunately, our monitoring noticed the low-performing campaign within minutes, and an alert was sent to the growth engineer on-call, who immediately reached out to the marketer and confirmed the change was unintentional, and then shut down the campaign.
Without this monitoring, a subtle targeting error like this could have gone unnoticed all weekend and would have eaten up $100,000+ of marketing budget. This episode shows that platform investment can benefit everyone; and since growth needs them most, it’s often the growth platform engineering team which implements them.
As the day-to-day work of a Growth Engineer shows, A/B tests are a critical tool to both measure success and learn. It’s a numbers game: the more A/B tests a team can run in a given quarter, the more of them will end up winners, making the team successful. It’s no wonder, then, that Growth Engineering will pull out all the stops to improve velocity.
3. Why Growth Engineers move faster than Product Engineers
On the surface, growth engineering teams look like product engineering ones; writing code, shipping pull requests, monitoring on-call, etc. So how do they move so much faster? The big reason lies in philosophy and focus, not technology. To quote Elena Verna, head of growth at Dropbox:
“Product Engineering teams ship to build; Growth Engineering teams ship to learn.”
Real-world case: price changes at Masterclass
A few years ago at MasterClass, the growth team wanted to see if changing our pricing model to multiple tiers would improve revenue.
Inspired in part by multiple pricing tiers for competitors such as Netflix (above), Disney Plus, and Hulu.
The “multiple pricing tier” proposal for MasterClass.
From a software engineering perspective, this was a highly complex project because:
- Backend engineering work: the backend did not yet support multiple pricing options, requiring a decent amount of engineering, and rigorous testing to make sure existing customers weren’t affected.
- Client app changes: on the device side, multiple platforms (iOS, iPad, Android, Roku, Apple TV, etc) would each need to be updated, including each relevant app store.
The software engineering team estimated that becoming a “multi-pricing-tier” company would take months across numerous engineering teams, and engineering leadership was unwilling to greenlight that significant investment.
We in growth engineering took this as a challenge. As usual, our goal was not just to add the new pricing model, but to learn how much money it might bring in. The approach we ended up proposing was a Fake Door test, which involves offering a not-yet-available option to customers to gauge interest level. This was risky, as taking a customer who’s ready to pay and telling them to join some kind of waiting list is a colossal waste, and risks making them feel like the target of a “bait and switch” trick.
We found a way. The key insight was that people are only offended about a “bait and switch”, if the “switch” is worse than the “bait.” Telling customers they would pay $100 and then switching to $150 would cause a riot, but starting at $150 and then saying “just kidding, it’s only $100” is a pleasant surprise.
The good kind of surprise.
So long as every test “pricing tier” is less appealing – higher prices, fewer features – than the current offering, we could “upgrade” customers after their initial selection. A customer choosing the cheapest tier gets extra features at no extra cost, while a customer choosing a more expensive tier is offered a discount.
We created three new tiers, at different prices. The new “premium” tier would describe the existing, original offering. Regardless of what potential customers selected, they got this “original offering,” during the experiment.
The best thing about this was that no backend changes were required. There were no real, new, back-end pricing plans; everybody ended up purchasing the same version of MasterClass for the same price, with the same features. The entirety of the engineering work was on building a new pricing page, and the “congratulations, you’ve been upgraded” popup. This took just a few days.
Within a couple of weeks, we had enough data to be confident the financial upside of moving to a multi-pricing-tier model would be significant. With this, we’re able to convince the rest of engineering’s leadership to invest in building the feature properly. In the end, launching multiple pricing tiers turned out to be one of the biggest revenue wins of the year.
Building a skyscraper vs building a tent
The MasterClass example demonstrates the spirit of growth engineering; focusing on building to learn, instead of building to last. Consider building skyscrapers versus tents.
Building a tent optimizes for speed of set-up and tear-down over longevity. You don’t think of a tent as one that is shoddy or low-quality compared to skyscrapers: it’s not even the same category of buildings! Growth engineers maximize use of lightweight materials. To stick with the tents vs skyscraper metaphor: we prioritize lightweight fabric materials over steel and concrete whenever possible. We only resort to traditional building materials when there’s no other choice, or when a direction is confirmed as correct. Quality is important – after all, a tent must keep out rain and mosquitoes. However, the speed-vs-durability tradeoff decision results in very different approaches and outcomes.
4. Tech stack
At first glance, growth and product engineers use the same tooling, and contribute to the same codebases. But growth engineering tends to be high-velocity, experiment-heavy, and with limited test coverage. This means that certain “nice to have” tools for product engineering are mission-critical for growth engineers.
Read more https://connect-test.layer3.press/articles/ea02c1a1-7cfa-42b4-8722-0165abcae8bb
-
 @ 3bf0c63f:aefa459d
2025-04-25 19:26:48
@ 3bf0c63f:aefa459d
2025-04-25 19:26:48Redistributing Git with Nostr
Every time someone tries to "decentralize" Git -- like many projects tried in the past to do it with BitTorrent, IPFS, ScuttleButt or custom p2p protocols -- there is always a lurking comment: "but Git is already distributed!", and then the discussion proceeds to mention some facts about how Git supports multiple remotes and its magic syncing and merging abilities and so on.
Turns out all that is true, Git is indeed all that powerful, and yet GitHub is the big central hub that hosts basically all Git repositories in the giant world of open-source. There are some crazy people that host their stuff elsewhere, but these projects end up not being found by many people, and even when they do they suffer from lack of contributions.
Because everybody has a GitHub account it's easy to open a pull request to a repository of a project you're using if it's on GitHub (to be fair I think it's very annoying to have to clone the repository, then add it as a remote locally, push to it, then go on the web UI and click to open a pull request, then that cloned repository lurks forever in your profile unless you go through 16 screens to delete it -- but people in general seem to think it's easy).
It's much harder to do it on some random other server where some project might be hosted, because now you have to add 4 more even more annoying steps: create an account; pick a password; confirm an email address; setup SSH keys for pushing. (And I'm not even mentioning the basic impossibility of offering
pushaccess to external unknown contributors to people who want to host their own simple homemade Git server.)At this point some may argue that we could all have accounts on GitLab, or Codeberg or wherever else, then those steps are removed. Besides not being a practical strategy this pseudo solution misses the point of being decentralized (or distributed, who knows) entirely: it's far from the ideal to force everybody to have the double of account management and SSH setup work in order to have the open-source world controlled by two shady companies instead of one.
What we want is to give every person the opportunity to host their own Git server without being ostracized. at the same time we must recognize that most people won't want to host their own servers (not even most open-source programmers!) and give everybody the ability to host their stuff on multi-tenant servers (such as GitHub) too. Importantly, though, if we allow for a random person to have a standalone Git server on a standalone server they host themselves on their wood cabin that also means any new hosting company can show up and start offering Git hosting, with or without new cool features, charging high or low or zero, and be immediately competing against GitHub or GitLab, i.e. we must remove the network-effect centralization pressure.
External contributions
The first problem we have to solve is: how can Bob contribute to Alice's repository without having an account on Alice's server?
SourceHut has reminded GitHub users that Git has always had this (for most) arcane
git send-emailcommand that is the original way to send patches, using an once-open protocol.Turns out Nostr acts as a quite powerful email replacement and can be used to send text content just like email, therefore patches are a very good fit for Nostr event contents.
Once you get used to it and the proper UIs (or CLIs) are built sending and applying patches to and from others becomes a much easier flow than the intense clickops mixed with terminal copypasting that is interacting with GitHub (you have to clone the repository on GitHub, then update the remote URL in your local directory, then create a branch and then go back and turn that branch into a Pull Request, it's quite tiresome) that many people already dislike so much they went out of their way to build many GitHub CLI tools just so they could comment on issues and approve pull requests from their terminal.
Replacing GitHub features
Aside from being the "hub" that people use to send patches to other people's code (because no one can do the email flow anymore, justifiably), GitHub also has 3 other big features that are not directly related to Git, but that make its network-effect harder to overcome. Luckily Nostr can be used to create a new environment in which these same features are implemented in a more decentralized and healthy way.
Issues: bug reports, feature requests and general discussions
Since the "Issues" GitHub feature is just a bunch of text comments it should be very obvious that Nostr is a perfect fit for it.
I will not even mention the fact that Nostr is much better at threading comments than GitHub (which doesn't do it at all), which can generate much more productive and organized discussions (and you can opt out if you want).
Search
I use GitHub search all the time to find libraries and projects that may do something that I need, and it returns good results almost always. So if people migrated out to other code hosting providers wouldn't we lose it?
The fact is that even though we think everybody is on GitHub that is a globalist falsehood. Some projects are not on GitHub, and if we use only GitHub for search those will be missed. So even if we didn't have a Nostr Git alternative it would still be necessary to create a search engine that incorporated GitLab, Codeberg, SourceHut and whatnot.
Turns out on Nostr we can make that quite easy by not forcing anyone to integrate custom APIs or hardcoding Git provider URLs: each repository can make itself available by publishing an "announcement" event with a brief description and one or more Git URLs. That makes it easy for a search engine to index them -- and even automatically download the code and index the code (or index just README files or whatever) without a centralized platform ever having to be involved.
The relays where such announcements will be available play a role, of course, but that isn't a bad role: each announcement can be in multiple relays known for storing "public good" projects, some relays may curate only projects known to be very good according to some standards, other relays may allow any kind of garbage, which wouldn't make them good for a search engine to rely upon, but would still be useful in case one knows the exact thing (and from whom) they're searching for (the same is valid for all Nostr content, by the way, and that's where it's censorship-resistance comes from).
Continuous integration
GitHub Actions are a very hardly subsidized free-compute-for-all-paid-by-Microsoft feature, but one that isn't hard to replace at all. In fact there exists today many companies offering the same kind of service out there -- although they are mostly targeting businesses and not open-source projects, before GitHub Actions was introduced there were also many that were heavily used by open-source projects.
One problem is that these services are still heavily tied to GitHub today, they require a GitHub login, sometimes BitBucket and GitLab and whatnot, and do not allow one to paste an arbitrary Git server URL, but that isn't a thing that is very hard to change anyway, or to start from scratch. All we need are services that offer the CI/CD flows, perhaps using the same framework of GitHub Actions (although I would prefer to not use that messy garbage), and charge some few satoshis for it.
It may be the case that all the current services only support the big Git hosting platforms because they rely on their proprietary APIs, most notably the webhooks dispatched when a repository is updated, to trigger the jobs. It doesn't have to be said that Nostr can also solve that problem very easily.
-
 @ b83a28b7:35919450
2025-05-16 19:26:56
@ b83a28b7:35919450
2025-05-16 19:26:56This article was originally part of the sermon of Plebchain Radio Episode 111 (May 2, 2025) that nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpqtvqc82mv8cezhax5r34n4muc2c4pgjz8kaye2smj032nngg52clq7fgefr and I did with nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7ct4w35zumn0wd68yvfwvdhk6tcqyzx4h2fv3n9r6hrnjtcrjw43t0g0cmmrgvjmg525rc8hexkxc0kd2rhtk62 and nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpq4wxtsrj7g2jugh70pfkzjln43vgn4p7655pgky9j9w9d75u465pqahkzd0 of the nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcqyqwfvwrccp4j2xsuuvkwg0y6a20637t6f4cc5zzjkx030dkztt7t5hydajn
Listen to the full episode here:
<<https://fountain.fm/episode/Ln9Ej0zCZ5dEwfo8w2Ho>>
Bitcoin has always been a narrative revolution disguised as code. White paper, cypherpunk lore, pizza‑day legends - every block is a paragraph in the world’s most relentless epic. But code alone rarely converts the skeptic; it’s the camp‑fire myth that slips past the prefrontal cortex and shakes hands with the limbic system. People don’t adopt protocols first - they fall in love with protagonists.
Early adopters heard the white‑paper hymn, but most folks need characters first: a pizza‑day dreamer; a mother in a small country, crushed by the cost of remittance; a Warsaw street vendor swapping złoty for sats. When their arcs land, the brain releases a neurochemical OP_RETURN which says, “I belong in this plot.” That’s the sly roundabout orange pill: conviction smuggled inside catharsis.
That’s why, from 22–25 May in Warsaw’s Kinoteka, the Bitcoin Film Fest is loading its reels with rebellion. Each documentary, drama, and animated rabbit‑hole is a stealth wallet, zipping conviction straight into the feels of anyone still clasped within the cold claw of fiat. You come for the plot, you leave checking block heights.
Here's the clip of the sermon from the episode:
nostr:nevent1qvzqqqqqqypzpwp69zm7fewjp0vkp306adnzt7249ytxhz7mq3w5yc629u6er9zsqqsy43fwz8es2wnn65rh0udc05tumdnx5xagvzd88ptncspmesdqhygcrvpf2
-
 @ 256a7941:b828ba8d
2024-08-14 01:27:30
@ 256a7941:b828ba8d
2024-08-14 01:27:30BITCOINERS NEED A REMINDER THAT ROSS ULBRICHT WAS A SELF-PROCLAIMED LIBERTARIAN. NOT DEMOCRAT. NOT REPUBLICAN
FREEROSS
originally posted at https://stacker.news/items/647883
-
 @ 8cb60e21:5f2deaea
2024-08-13 21:22:05
@ 8cb60e21:5f2deaea
2024-08-13 21:22:05Title
subtitle
subsub
some Code some code: ```js import NextAuth from "next-auth"; import CredentialsProvider from "next-auth/providers/credentials"; import NDK from "@nostr-dev-kit/ndk"; import axios from "axios"; import { findKind0Fields } from "@/utils/nostr";
const relayUrls = [ "wss://nos.lol/", "wss://relay.damus.io/", "wss://relay.snort.social/", "wss://relay.nostr.band/", "wss://nostr.mutinywallet.com/", "wss://relay.mutinywallet.com/", "wss://relay.primal.net/" ];
const BASE_URL = process.env.BASE_URL;
const ndk = new NDK({ explicitRelayUrls: relayUrls, });
const authorize = async (pubkey) => { await ndk.connect(); const user = ndk.getUser({ pubkey });
try { const profile = await user.fetchProfile(); // Check if user exists, create if not const response = await axios.get(`${BASE_URL}/api/users/${pubkey}`); if (response.status === 200 && response.data) { const fields = await findKind0Fields(profile); // Combine user object with kind0Fields, giving priority to kind0Fields const combinedUser = { ...fields, ...response.data }; // Update the user on the backend if necessary // await axios.put(`${BASE_URL}/api/users/${combinedUser.id}`, combinedUser); return combinedUser; } else if (response.status === 204) { // Create user if (profile) { const fields = await findKind0Fields(profile); console.log('FEEEEELDS', fields); const payload = { pubkey, ...fields }; const createUserResponse = await axios.post(`${BASE_URL}/api/users`, payload); return createUserResponse.data; } } } catch (error) { console.error("Nostr login error:", error); } return null;}
export default NextAuth({ providers: [ CredentialsProvider({ id: "nostr", name: "Nostr", credentials: { pubkey: { label: "Public Key", type: "text" }, }, authorize: async (credentials) => { if (credentials?.pubkey) { return await authorize(credentials.pubkey); } return null; }, }), ], callbacks: { async jwt({ token, trigger, user }) { console.log('TRIGGER', trigger); if (trigger === "update") { // if we trigger an update call the authorize function again const newUser = await authorize(token.user.pubkey); token.user = newUser; } // Add combined user object to the token if (user) { token.user = user; } return token; }, async session({ session, token }) { // Add user from token to session session.user = token.user; session.jwt = token; return session; }, async redirect({ url, baseUrl }) { return baseUrl; }, async signOut({ token, session }) { console.log('signOut', token, session); token = {} session = {} return true }, }, secret: process.env.NEXTAUTH_SECRET, session: { strategy: "jwt" }, jwt: { signingKey: process.env.JWT_SECRET, }, pages: { signIn: "/auth/signin", }, }); ```
-
 @ b83a28b7:35919450
2025-05-16 19:23:58
@ b83a28b7:35919450
2025-05-16 19:23:58This article was originally part of the sermon of Plebchain Radio Episode 110 (May 2, 2025) that nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpqtvqc82mv8cezhax5r34n4muc2c4pgjz8kaye2smj032nngg52clq7fgefr and I did with nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7ct4w35zumn0wd68yvfwvdhk6tcqyzx4h2fv3n9r6hrnjtcrjw43t0g0cmmrgvjmg525rc8hexkxc0kd2rhtk62 and nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpq4wxtsrj7g2jugh70pfkzjln43vgn4p7655pgky9j9w9d75u465pqahkzd0 of the nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcqyqwfvwrccp4j2xsuuvkwg0y6a20637t6f4cc5zzjkx030dkztt7t5hydajn
Listen to the full episode here:
<https://fountain.fm/episode/Ln9Ej0zCZ5dEwfo8w2Ho>
Bitcoin has always been a narrative revolution disguised as code. White paper, cypherpunk lore, pizza‑day legends - every block is a paragraph in the world’s most relentless epic. But code alone rarely converts the skeptic; it’s the camp‑fire myth that slips past the prefrontal cortex and shakes hands with the limbic system. People don’t adopt protocols first - they fall in love with protagonists.
Early adopters heard the white‑paper hymn, but most folks need characters first: a pizza‑day dreamer; a mother in a small country, crushed by the cost of remittance; a Warsaw street vendor swapping złoty for sats. When their arcs land, the brain releases a neurochemical OP_RETURN which says, “I belong in this plot.” That’s the sly roundabout orange pill: conviction smuggled inside catharsis.
That’s why, from 22–25 May in Warsaw’s Kinoteka, the Bitcoin Film Fest is loading its reels with rebellion. Each documentary, drama, and animated rabbit‑hole is a stealth wallet, zipping conviction straight into the feels of anyone still clasped within the cold claw of fiat. You come for the plot, you leave checking block heights.
Here's the clip of the sermon from the episode:
nostr:nevent1qvzqqqqqqypzpwp69zm7fewjp0vkp306adnzt7249ytxhz7mq3w5yc629u6er9zsqqsy43fwz8es2wnn65rh0udc05tumdnx5xagvzd88ptncspmesdqhygcrvpf2
-
 @ 3bf0c63f:aefa459d
2025-04-25 18:55:52
@ 3bf0c63f:aefa459d
2025-04-25 18:55:52Report of how the money Jack donated to the cause in December 2022 has been misused so far.
Bounties given
March 2025
- Dhalsim: 1,110,540 - Work on Nostr wiki data processing
February 2025
- BOUNTY* NullKotlinDev: 950,480 - Twine RSS reader Nostr integration
- Dhalsim: 2,094,584 - Work on Hypothes.is Nostr fork
- Constant, Biz and J: 11,700,588 - Nostr Special Forces
January 2025
- Constant, Biz and J: 11,610,987 - Nostr Special Forces
- BOUNTY* NullKotlinDev: 843,840 - Feeder RSS reader Nostr integration
- BOUNTY* NullKotlinDev: 797,500 - ReadYou RSS reader Nostr integration
December 2024
- BOUNTY* tijl: 1,679,500 - Nostr integration into RSS readers yarr and miniflux
- Constant, Biz and J: 10,736,166 - Nostr Special Forces
- Thereza: 1,020,000 - Podcast outreach initiative
November 2024
- Constant, Biz and J: 5,422,464 - Nostr Special Forces
October 2024
- Nostrdam: 300,000 - hackathon prize
- Svetski: 5,000,000 - Latin America Nostr events contribution
- Quentin: 5,000,000 - nostrcheck.me
June 2024
- Darashi: 5,000,000 - maintaining nos.today, searchnos, search.nos.today and other experiments
- Toshiya: 5,000,000 - keeping the NIPs repo clean and other stuff
May 2024
- James: 3,500,000 - https://github.com/jamesmagoo/nostr-writer
- Yakihonne: 5,000,000 - spreading the word in Asia
- Dashu: 9,000,000 - https://github.com/haorendashu/nostrmo
February 2024
- Viktor: 5,000,000 - https://github.com/viktorvsk/saltivka and https://github.com/viktorvsk/knowstr
- Eric T: 5,000,000 - https://github.com/tcheeric/nostr-java
- Semisol: 5,000,000 - https://relay.noswhere.com/ and https://hist.nostr.land relays
- Sebastian: 5,000,000 - Drupal stuff and nostr-php work
- tijl: 5,000,000 - Cloudron, Yunohost and Fraidycat attempts
- Null Kotlin Dev: 5,000,000 - AntennaPod attempt
December 2023
- hzrd: 5,000,000 - Nostrudel
- awayuki: 5,000,000 - NOSTOPUS illustrations
- bera: 5,000,000 - getwired.app
- Chris: 5,000,000 - resolvr.io
- NoGood: 10,000,000 - nostrexplained.com stories
October 2023
- SnowCait: 5,000,000 - https://nostter.vercel.app/ and other tools
- Shaun: 10,000,000 - https://yakihonne.com/, events and work on Nostr awareness
- Derek Ross: 10,000,000 - spreading the word around the world
- fmar: 5,000,000 - https://github.com/frnandu/yana
- The Nostr Report: 2,500,000 - curating stuff
- james magoo: 2,500,000 - the Obsidian plugin: https://github.com/jamesmagoo/nostr-writer
August 2023
- Paul Miller: 5,000,000 - JS libraries and cryptography-related work
- BOUNTY tijl: 5,000,000 - https://github.com/github-tijlxyz/wikinostr
- gzuus: 5,000,000 - https://nostree.me/
July 2023
- syusui-s: 5,000,000 - rabbit, a tweetdeck-like Nostr client: https://syusui-s.github.io/rabbit/
- kojira: 5,000,000 - Nostr fanzine, Nostr discussion groups in Japan, hardware experiments
- darashi: 5,000,000 - https://github.com/darashi/nos.today, https://github.com/darashi/searchnos, https://github.com/darashi/murasaki
- jeff g: 5,000,000 - https://nostr.how and https://listr.lol, plus other contributions
- cloud fodder: 5,000,000 - https://nostr1.com (open-source)
- utxo.one: 5,000,000 - https://relaying.io (open-source)
- Max DeMarco: 10,269,507 - https://www.youtube.com/watch?v=aA-jiiepOrE
- BOUNTY optout21: 1,000,000 - https://github.com/optout21/nip41-proto0 (proposed nip41 CLI)
- BOUNTY Leo: 1,000,000 - https://github.com/leo-lox/camelus (an old relay thing I forgot exactly)
June 2023
- BOUNTY: Sepher: 2,000,000 - a webapp for making lists of anything: https://pinstr.app/
- BOUNTY: Kieran: 10,000,000 - implement gossip algorithm on Snort, implement all the other nice things: manual relay selection, following hints etc.
- Mattn: 5,000,000 - a myriad of projects and contributions to Nostr projects: https://github.com/search?q=owner%3Amattn+nostr&type=code
- BOUNTY: lynn: 2,000,000 - a simple and clean git nostr CLI written in Go, compatible with William's original git-nostr-tools; and implement threaded comments on https://github.com/fiatjaf/nocomment.
- Jack Chakany: 5,000,000 - https://github.com/jacany/nblog
- BOUNTY: Dan: 2,000,000 - https://metadata.nostr.com/
April 2023
- BOUNTY: Blake Jakopovic: 590,000 - event deleter tool, NIP dependency organization
- BOUNTY: koalasat: 1,000,000 - display relays
- BOUNTY: Mike Dilger: 4,000,000 - display relays, follow event hints (Gossip)
- BOUNTY: kaiwolfram: 5,000,000 - display relays, follow event hints, choose relays to publish (Nozzle)
- Daniele Tonon: 3,000,000 - Gossip
- bu5hm4nn: 3,000,000 - Gossip
- BOUNTY: hodlbod: 4,000,000 - display relays, follow event hints
March 2023
- Doug Hoyte: 5,000,000 sats - https://github.com/hoytech/strfry
- Alex Gleason: 5,000,000 sats - https://gitlab.com/soapbox-pub/mostr
- verbiricha: 5,000,000 sats - https://badges.page/, https://habla.news/
- talvasconcelos: 5,000,000 sats - https://migrate.nostr.com, https://read.nostr.com, https://write.nostr.com/
- BOUNTY: Gossip model: 5,000,000 - https://camelus.app/
- BOUNTY: Gossip model: 5,000,000 - https://github.com/kaiwolfram/Nozzle
- BOUNTY: Bounty Manager: 5,000,000 - https://nostrbounties.com/
February 2023
- styppo: 5,000,000 sats - https://hamstr.to/
- sandwich: 5,000,000 sats - https://nostr.watch/
- BOUNTY: Relay-centric client designs: 5,000,000 sats https://bountsr.org/design/2023/01/26/relay-based-design.html
- BOUNTY: Gossip model on https://coracle.social/: 5,000,000 sats
- Nostrovia Podcast: 3,000,000 sats - https://nostrovia.org/
- BOUNTY: Nostr-Desk / Monstr: 5,000,000 sats - https://github.com/alemmens/monstr
- Mike Dilger: 5,000,000 sats - https://github.com/mikedilger/gossip
January 2023
- ismyhc: 5,000,000 sats - https://github.com/Galaxoid-Labs/Seer
- Martti Malmi: 5,000,000 sats - https://iris.to/
- Carlos Autonomous: 5,000,000 sats - https://github.com/BrightonBTC/bija
- Koala Sat: 5,000,000 - https://github.com/KoalaSat/nostros
- Vitor Pamplona: 5,000,000 - https://github.com/vitorpamplona/amethyst
- Cameri: 5,000,000 - https://github.com/Cameri/nostream
December 2022
- William Casarin: 7 BTC - splitting the fund
- pseudozach: 5,000,000 sats - https://nostr.directory/
- Sondre Bjellas: 5,000,000 sats - https://notes.blockcore.net/
- Null Dev: 5,000,000 sats - https://github.com/KotlinGeekDev/Nosky
- Blake Jakopovic: 5,000,000 sats - https://github.com/blakejakopovic/nostcat, https://github.com/blakejakopovic/nostreq and https://github.com/blakejakopovic/NostrEventPlayground
-
 @ 8e7462a8:c723a97b
2024-08-13 21:12:24
@ 8e7462a8:c723a97b
2024-08-13 21:12:24Here's some code!
```js import React, { useEffect, useState } from "react"; import { useNDKContext } from "@/context/NDKContext"; import { parseEvent } from "@/utils/nostr"; import { ProgressSpinner } from "primereact/progressspinner";
const PurchasedListItem = ({ eventId, category }) => { const { ndk } = useNDKContext(); const [event, setEvent] = useState(null);
useEffect(() => { const fetchEvent = async () => { if (!eventId) return; try { await ndk.connect(); const event = await ndk.fetchEvent(eventId); if (event) { setEvent(parseEvent(event)); } } catch (error) { console.error("Error fetching event:", error); } } fetchEvent(); }, [eventId, ndk]); return !event || !ndk ? <ProgressSpinner className="w-[40px] h-[40px]" /> : (<a className="text-blue-500 underline hover:text-blue-600" href={category === "courses" ? `/courses/${event.id}` : `/details/${event.id}`}>{event.title}</a>);}
export default PurchasedListItem; ```
-
 @ 502ab02a:a2860397
2025-05-23 07:35:13
@ 502ab02a:a2860397
2025-05-23 07:35:13แหม่ ต้องรีบแวะมาเขียนไว้ก่อน ของกำลังร้อนๆ #ตัวหนังสือมีเสียง เพลง ลานกรองมันส์ นั้นเรื่องที่มาที่ไปน่าจะไปตามอ่านในเพจ ลานกรองมันส์ ได้ครับ recap คร่าวๆคือมันคือ พื้นที่สร้างสรรค์ที่เปิดให้มาทำกิจกรรมต่างๆนานากันได้ครับ
วันนี้เลยจะมาเล่าเรื่องวิธีการใช้คำ ซึ่งมันส์ดีตามชื่อลาน ฮาๆๆๆ ผมตั้งโจทย์ไว้เลยว่า ต้องมีคำว่า ลานกรองมันส์ แน่ๆแล้ว เพราะเป็นชื่อสถานที่ จากนั้นก็เอาคำว่า ลานกองมัน มาแตกขยายความเพราะมันคือต้นกำเนิดเดิมของพื้นที่นั้น คือเป็นลานที่เอาหัวมันมากองกันเอาไว้ รอนำไปผลิตต่อเป็นสินค้าการเกษตรต่างๆ
ตอนนี้เขาเลิกทำไปแล้ว จึงกลายมาเป็น ลานกรองมันส์ ที่เอาชื่อเดิมมาแปลง
เมื่อได้คำหลักๆแล้วผมก็เอาพยัญชนะเลย ลอลิง กอไก่ มอม้า คือตัวหลักของเพลง
โทนดนตรีไม่ต้องเลือกเลยหนีไม่พ้นสามช่าแน่นอน โทนมันมาตั้งแต่เริ่มคิดจะเขียนเลยครับ ฮาๆๆๆ
ผมพยายามแบ่งวรรคไว้ชัดๆ เผื่อไว้เลยว่าอนาคตอาจมีการทำดนตรีแบบแบ่งกันร้อง วรรคของมันเลยเป็น หมู่ เดี่ยว หมู่ เดี่ยว หมู่ เดี่ยว หมู่ แบบสามโทนเลย
ท่อนหมู่นั้น คิดแบบหลายชั้นมากครับ โดยเฉพาะคำว่า มัน เอามันมากอง มันที่ว่าได้ทั้งเป็นคำกิริยา คือ เอามันมากองๆ หรือ มันที่ว่าอาจหมายถึงตัวความฝันเองเป็นคำลักษณะนามเรียกความฝัน "ลานกรองมันส์ เรามาลองกัน มาร่วมกันมอง ลานกรองมันส์ มาร่วมสร้างฝัน เอามันมากอง"
หรือแม้แต่ท่อนต่างๆ ก็เล่นคำว่า มัน กอง เพื่อให้รู้สึกย้ำท่อนหมู่ ที่มีคำว่ามัน เป็นพระเอกหลายหน้า ทั้งความสนุก ทั้งลักษณะนามความฝัน ทั้งกิริยา "ทุกคน ต่างมี ความฝัน เอามา รวมกัน ให้มันเป็นกอง"
อีกท่อนที่ชอบมากตอนเขียนคือ ทำที่ ลานกรองมันส์ idea for fun everyone can do เพราะรู้สึกว่า การพูดภาษาอังกฤษสำเนียงไทยๆ มันตูดหมึกดี ฮาๆๆๆๆ
หัวใจของเพลงคือจะบอกว่า ใครมีฝันก็มาเลย มาทำฝันกัน เรามีที่ให้คุณ ไม่ต้องกลัวอะไรที่จะทำฝันของตัวเอง เล็กใหญ่ ผิดถูก ขอให้ทำมัน อย่าให้ใครหยุดฝันของคุณ นอกจากตัวคุณเอง
เพลงนี้ไม่ได้ลงแพลทฟอร์ม เพราะส่งมอบให้ทาง ลานกรองมันส์เขาครับ ใช้ตามอิสระไปเลย ดังนั้นก็อาจต้องฟังในโพสนี้ หรือ ในยูทูปนะครับ https://youtu.be/W-1OH3YldtM?si=36dFbHgKjiI_9DI8
เนื้อเพลง "ลานกรองมันส์"
ลานกรองมันส์ ขอเชิญทุกท่าน มามันกันดู นะโฉมตรู มาลองดูกัน อ๊ะ มาลันดูกอง
มีงาน คุยกัน สังสรรค์ ดื่มนม ชมจันทร์ ปันฝัน กันเพลิน ทุกคน ต่างล้วน มีดี เรานั้น มีที่ พี่นี้มีโชว์ เอ้า
ลานกรองมันส์ เรามาลองกัน มาร่วมกันมอง ลานกรองมันส์ มาร่วมสร้างฝัน เอามันมากอง
จะเล็ก จะใหญ่ ให้ลอง เราเป็น พี่น้อง เพื่อนพ้อง ต้องตา ทุกคน ต่างมี ความฝัน เอามา รวมกัน ให้มันเป็นกอง เอ้า
ลานกรองมันส์ เรามาลองกัน มาร่วมกันมอง ลานกรองมันส์ มาร่วมสร้างฝัน เอามันมากอง
ชีวิต เราคิดเราทำ ทุกสิ่งที่ย้ำ คือทำสุดใจ จะเขียน จะเรียน จะรำ ทำที่ ลานกรองมันส์ idea for fun everyone can do
ลานกรองมันส์ เรามาลองกัน มาร่วมกันมอง ลานกรองมันส์ มาร่วมสร้างฝัน เอามันมากอง
เรามา ลั่นกลองให้มัน เฮไหนเฮกัน ที่ลานกรองมันส์ ให้ฝัน บันเทิง…
ตัวหนังสือมีเสียง #pirateketo #siamstr
-
 @ 04c915da:3dfbecc9
2025-05-16 18:06:46
@ 04c915da:3dfbecc9
2025-05-16 18:06:46Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Using stolen bitcoin for the reserve creates a perverse incentive. If governments see bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 04c915da:3dfbecc9
2025-03-26 20:54:33
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 6bae33c8:607272e8
2024-08-13 20:48:15
@ 6bae33c8:607272e8
2024-08-13 20:48:15BCL2 took place today. I drew the third pick.
Here are the results:
1.3 Ja’Marr Chase — I didn’t want Christian McCalfinjury, of whom I already have a share, so I was set on CeeDee Lamb or Tyreek Hill if they were there. But I had an inkling they might go 1-2 in which case Ja’Marr Chase was narrowly my fallback over Amon Ra St. Brown and Breece Hall. Chase has St. Brown’s target upside, but with a much bigger vertical game. The biggest negative for him is Burrow’s health, but Burrow’s fine now, and anyone can get hurt. I also thought maybe I’d draft Tee Higgins if he fell to me in Round 5 (which was unlikely) in which case I’d try to get Burrow too.
2.10 Jaylen Waddle — It was Waddle the solid, boring pick or Malik Nabers the fun, exciting one. Team 4 did me a favor and took De’Von Achane out of the equation — I have Achane in BCL1, and while I love his upside, he’s not the kind of player to which you tie all your teams. I narrowly went Waddle who actually has upside too if Tyreek Hill ever got hurt.
3.10 Malik Nabers — I couldn’t believe it, but Nabers made it all the way back despite third-round reversal. I love Nabers, but I think the market is over-drafting him slightly relative to his projected target share. I mean he might get 150, but I think 130-140 Daniel Jones targets is more likely, and that’s a third, not a second-round pick. ** 4.3 Stefon Diggs** — This was going perfectly. Had Nabers been taken, I would have gone Diggs in Round 3, but he was still there four picks later. I’ve mentioned before I have Diggs as a top-10-ish WR.
5.10 Anthony Richardson — I took Reachardson early because I didn’t need another receiver (would be my first bench spot), the running back I liked best was still likely to be back in Round 6 too, and I couldn’t bring myself to take Kyle Pitts who has burned me so many times. ** 6.3 Rhamondre Stevenson** — Backs were flying off the board in this draft which figures because I went so WR-heavy, but I think Stevenson is good, and there’s no way the Patriots offense won’t be better than last year’s just from pure regression to the mean.
7.10 Javonte Williams — Another good back on a bad team, Williams’ 2023 was not representative given he was only one year removed from an ACL tear. We should see the real version this year, and I expect him to be the main guy in Denver. ** 8.3 Ladd McConkey** — This was a luxury pick, but I liked the value too much, and I wasn’t in love with any of the RB or TE at cost. (I missed out on Jake Ferguson right after the Williams pick.) But the McConkey pick cost me Zack Moss, Devin Singletary, Nick Chubb, Brian Robinson, Chase Brown, Blake Corum and Tyjae Spears.
9.10 Brock Bowers — I missed out on David Njoku by one pick too, so it was time to get Bowers, the last of that tier of tight ends.
10.3 Jerome Ford — He’s Nick Chubb’s backup at worst, and that assumes Chubb will even be at full health any time soon.
11.10 Rashid Shaheed — Another luxury pick, but I couldn’t pass him up here. I’ve mentioned many times, I think he’s as good as Chris Olave, and there are only two of them now, so Shaheed should see his share of targets, either way. Shaheed cost me Zach Charbonnet and Cole Kmet though.
12.3 J.K. Dobbins — I’m not a big Gus Edwards believer — he’s 29 and with a limited skill set. Dobbins can never stay healthy, but worth a flyer here on what should be a run-heavy offense.
13.10 Kimani Vidal — Sounds like a high-end hair salon, but he’s actually the fallback if Dobbins and Edwards don’t pan out. I like his build (5-8, 215), speed and pass-catching skills.
14.3 Bucky Irving — I’m not sold on Rachaad White being anything special, and Irving is his backup. I needed a lot of lottery ticket backs with this build. ** 15.10 Khalil Herbert** — There are rumors he could be moved, but either way, I don’t trust D’Andre Soft, and Roschon Johnson is just a guy.
16.3 Jonnu Smith — This was a bit early per ADP, but I needed a second TE, and Smith has a lot of upside in an offense that’s so top heavy.
17.10 Justin Fields — In the likely event Russell Wilson is cooked, Fields is a top-10 fantasy quarterback already. I thought about Danny Dimes too. ** 18.3 Younghoe Koo** — I’m tired of drafting Justin Tucker every year, felt it was time for a Younghoe.
19.10 Giants Defense — They get the Sam Darnold Vikings in Week 1, the Football Team in Week 2. And they now have three elite pass rushers in Kayvon Thibodeaux, Dexter Lawrence and Brian Burns.
20.3 Roman Wilson — I wanted to take Danny Dimes, but Wilson could easily be the Steelers’ slot guy — Van Jefferson is bad, and even George Pickens is more of a highlight-reel guy who doesn’t command massive target share.
Roster By Position
QB Anthony Richardson
RB Rhamondre Stevenson/Javonte Williams
WR Ja’Marr Chase/Jaylen Waddle/Malik Nabers
TE Brock Bowers
FLEX Stefon Diggs
K Younghoe Koo
D Giants
B Ladd McConkey/Jerome Ford/Rashid Shaheed/J.K. Dobbins/Kimani Vidal/Bucky Irving/Khalil Herbert/Jonnu Smith/Justin Fields/Roman Wilson
-
 @ 04c915da:3dfbecc9
2025-05-16 17:59:23
@ 04c915da:3dfbecc9
2025-05-16 17:59:23Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 8f69ac99:4f92f5fd
2025-04-23 14:39:01
@ 8f69ac99:4f92f5fd
2025-04-23 14:39:01Dizem-nos que a inflação é necessária. Mas e se for, afinal, a raiz da disfunção económica que enfrentamos?
A crença mainstream é clara: para estimular o crescimento, os governos devem poder desvalorizar a sua moeda — essencialmente, criar dinheiro do nada. Supostamente, isso incentiva o investimento, aumenta o consumo e permite responder a crises económicas. Esta narrativa foi repetida tantas vezes que se tornou quase um axioma — raramente questionado.
No centro desta visão está a lógica fiat-keynesiana: uma economia estável exige um banco central disposto a manipular o valor do dinheiro para alcançar certos objectivos políticos. Esta abordagem, inspirada por John Maynard Keynes, defende a intervenção estatal como forma de estabilizar a economia durante recessões. Na teoria, os investidores e consumidores beneficiam de taxas de juro artificiais e de maior poder de compra — um suposto ganho para todos.
Mas há outra perspectiva: a visão do dinheiro sólido (sound money, em inglês). Enraizada na escola austríaca e nos princípios da liberdade individual, esta defende que a manipulação monetária não é apenas desnecessária — é prejudicial. Uma moeda estável, não sujeita à depreciação arbitrária, é essencial para promover trocas voluntárias, empreendedorismo e crescimento económico genuíno.
Está na hora de desafiar esta sabedoria convencional. Ao longo dos próximos capítulos, vamos analisar os pressupostos errados que sustentam a lógica fiat-keynesiana e explorar os benefícios de um sistema baseado em dinheiro sólido — como Bitcoin. Vamos mostrar por que desvalorizar a moeda é moralmente questionável e economicamente prejudicial, e propor alternativas mais éticas e eficazes.
Este artigo (que surge em resposta ao "guru" Miguel Milhões) pretende iluminar as diferenças entre estas duas visões opostas e apresentar uma abordagem mais sólida e justa para a política económica — centrada na liberdade pessoal, na responsabilidade individual e na preservação de instituições financeiras saudáveis.
O Argumento Fiat: Por que Dizem que é Preciso Desvalorizar a Moeda
Este argumento parte geralmente de uma visão económica keynesiana e/ou estatista e assenta em duas ideias principais: o incentivo ao investimento e a necessidade de resposta a emergências.
Incentivo ao Investimento
Segundo os defensores do sistema fiat, se uma moeda como o ouro ou bitcoin valorizar ao longo do tempo, as pessoas tenderão a "acumular" essa riqueza em vez de investir em negócios produtivos. O receio é que, se guardar dinheiro se torna mais rentável do que investir, a economia entre em estagnação.
Esta ideia parte de uma visão simplista do comportamento humano. Na realidade, as pessoas tomam decisões financeiras com base em múltiplos factores. Embora seja verdade que activos valorizáveis são atractivos, isso não significa que os investimentos desapareçam. Pelo contrário, o surgimento de activos como bitcoin cria novas oportunidades de inovação e investimento.
Historicamente, houve crescimento económico em períodos de moeda sólida — como no padrão-ouro. Uma moeda estável e previsível pode incentivar o investimento, ao dar confiança nos retornos futuros.
Resposta a Emergências
A segunda tese é que os governos precisam de imprimir dinheiro rapidamente em tempos de crise — pandemias, guerras ou recessões. Esta capacidade de intervenção é vista como essencial para "salvar" a economia.
De acordo com economistas keynesianos, uma injecção rápida de liquidez pode estabilizar a economia e evitar colapsos sociais. No entanto, este argumento ignora vários pontos fundamentais:
- A política monetária não substitui a responsabilidade fiscal: A capacidade de imprimir dinheiro não torna automaticamente eficaz o estímulo económico.
- A inflação é uma consequência provável: A impressão de dinheiro pode levar a pressões inflacionistas, reduzindo o poder de compra dos consumidores e minando o próprio estímulo pretendido. Estamos agora a colher os "frutos" da impressão de dinheiro durante a pandemia.
- O timing é crítico: Intervenções mal cronometradas podem agravar a situação.
Veremos em seguida porque estes argumentos não se sustentam.
Rebatendo os Argumentos
O Investimento Não Morre num Sistema de Dinheiro Sólido
O argumento de que o dinheiro sólido mata o investimento falha em compreender a ligação entre poupança e capital. Num sistema sólido, a poupança não é apenas acumulação — é capital disponível para financiar novos projectos. Isso conduz a um crescimento mais sustentável, baseado na qualidade e não na especulação.
Em contraste, o sistema fiat, com crédito barato, gera bolhas e colapsos — como vimos em 2008 ou na bolha dot-com. Estes exemplos ilustram os perigos da especulação facilitada por políticas monetárias artificiais.
Já num sistema de dinheiro sólido, como o que cresce em torno de Bitcoin, vemos investimentos em mineração, startups, educação e arte. Os investidores continuam activos — mas fazem escolhas mais responsáveis e de longo prazo.
Imprimir Dinheiro Não Resolve Crises
A ideia de que imprimir dinheiro é essencial em tempos de crise parte de uma ilusão perigosa. A inflação que se segue reduz o poder de compra e afecta especialmente os mais pobres — é uma forma oculta de imposto.
Além disso, soluções descentralizadas — como os mercados, redes comunitárias e poupança — são frequentemente mais eficazes. A resposta à COVID-19 ilustra isso: grandes empresas foram salvas, mas pequenos negócios e famílias ficaram para trás. Os últimos receberam um amuse-bouche, enquanto os primeiros comeram o prato principal, sopa, sobremesa e ainda levaram os restos.
A verdade é que imprimir dinheiro não cria valor — apenas o redistribui injustamente. A verdadeira resiliência nasce de comunidades organizadas e de uma base económica saudável, não de decretos políticos.
Dois Mundos: Fiat vs. Dinheiro Sólido
| Dimensão | Sistema Fiat-Keynesiano | Sistema de Dinheiro Sólido | |----------|--------------------------|-----------------------------| | Investimento | Estimulado por crédito fácil, alimentando bolhas | Baseado em poupança real e oportunidades sustentáveis | | Resposta a crises | Centralizada, via impressão de moeda | Descentralizada, baseada em poupança e solidariedade | | Preferência temporal | Alta: foco no consumo imediato | Baixa: foco na poupança e no futuro | | Distribuição de riqueza | Favorece os próximos ao poder (Efeito Cantillon) | Benefícios da deflação são distribuídos de forma mais justa | | Fundamento moral | Coercivo e redistributivo | Voluntário e baseado na liberdade individual |
Estes contrastes mostram que a escolha entre os dois sistemas vai muito além da economia — é também uma questão ética.
Consequências de Cada Sistema
O Mundo Fiat
Num mundo dominado pelo sistema fiat, os ciclos de euforia e colapso são a norma. A desigualdade aumenta, com os mais próximos ao poder a lucrar com a inflação e a impressão de dinheiro. A poupança perde valor, e a autonomia financeira das pessoas diminui.
À medida que o Estado ganha mais controlo sobre a economia, os cidadãos perdem capacidade de escolha e dependem cada vez mais de apoios governamentais. Esta dependência destrói o espírito de iniciativa e promove o conformismo.
O resultado? Estagnação, conflitos sociais e perda de liberdade.
O Mundo com Dinheiro Sólido
Com uma moeda sólida, o crescimento é baseado em valor real. As pessoas poupam mais, investem melhor e tornam-se mais independentes financeiramente. As comunidades tornam-se mais resilientes, e a cooperação substitui a dependência estatal.
Benefícios chave:
- Poupança real: A moeda não perde valor, e a riqueza pode ser construída com estabilidade.
- Resiliência descentralizada: Apoio mútuo entre indivíduos e comunidades em tempos difíceis.
- Liberdade económica: Menor interferência política e mais espaço para inovação e iniciativa pessoal.
Conclusão
A desvalorização da moeda não é uma solução — é um problema. Os sistemas fiat estão desenhados para transferir riqueza e poder de forma opaca, perpetuando injustiças e instabilidade.
Por outro lado, o dinheiro sólido — como Bitcoin — oferece uma alternativa credível e ética. Promove liberdade, responsabilidade e transparência. Impede abusos de poder e expõe os verdadeiros custos da má governação.
Não precisamos de mais inflação — precisamos de mais integridade.
Está na hora de recuperarmos o controlo sobre a nossa vida financeira. De rejeitarmos os sistemas que nos empobrecem lentamente e de construirmos um futuro em que o dinheiro serve as pessoas — e não os interesses políticos.
O futuro do dinheiro pode e deve ser diferente. Juntos, podemos criar uma economia mais justa, livre e resiliente — onde a prosperidade é partilhada e a dignidade individual respeitada.
Photo by rc.xyz NFT gallery on Unsplash
-
 @ 502ab02a:a2860397
2025-05-23 01:57:14
@ 502ab02a:a2860397
2025-05-23 01:57:14น้ำนมมนุษย์ที่ไม่ง้อมนุษย์ หรือนี่กำลังจะกลายเป็นเรื่องจริงเร็วกว่าที่เราคิดนะครับ
ในยุคที่อุตสาหกรรมอาหารหันหลังให้กับปศุสัตว์ ไม่ว่าจะด้วยเหตุผลด้านสิ่งแวดล้อม จริยธรรม หรือความยั่งยืน “น้ำนมจากห้องแล็บ” กำลังกลายเป็นแนวหน้าของการปฏิวัติอาหาร โดยเฉพาะเมื่อบริษัทหนึ่งจากสิงคโปร์นามว่า TurtleTree ประกาศอย่างชัดเจนว่า พวกเขากำลังจะสร้างโปรตีนสำคัญในน้ำนมมนุษย์ โดยไม่ต้องมีมนุษย์แม่เลยแม้แต่น้อย
TurtleTree ก่อตั้งในปี 2019 โดยมีเป้าหมายอันทะเยอทะยานคือการผลิตโปรตีนในนมแม่ให้ได้ผ่านเทคโนโลยีที่เรียกว่า precision fermentation โดยใช้จุลินทรีย์ที่ถูกดัดแปลงพันธุกรรมให้ผลิตโปรตีนเฉพาะ เช่น lactoferrin และ human milk oligosaccharides (HMOs) ซึ่งเป็นองค์ประกอบล้ำค่าที่พบในน้ำนมมนุษย์แต่แทบไม่มีในนมวัว หรือผลิตภัณฑ์นมทั่วไป
โปรตีนตัวแรกที่ TurtleTree ประสบความสำเร็จในการผลิตคือ LF+ หรือ lactoferrin ที่เลียนแบบโปรตีนในนมแม่ ซึ่งมีหน้าที่ช่วยระบบภูมิคุ้มกันของทารก ต่อต้านแบคทีเรีย และช่วยให้ร่างกายดูดซึมธาตุเหล็กได้ดีขึ้น โปรตีนนี้เป็นหนึ่งในหัวใจของนมแม่ ที่บริษัทต้องการนำมาใช้ในอุตสาหกรรมนมผงเด็กและอาหารเสริมสำหรับผู้ใหญ่ ล่าสุดในปี 2024 LF+ ได้รับการรับรองสถานะ GRAS (Generally Recognized As Safe) จากองค์การอาหารและยาสหรัฐฯ (FDA) อย่างเป็นทางการ เป็นหมุดหมายสำคัญที่บอกว่า นี่ไม่ใช่แค่ไอเดียในแล็บอีกต่อไป แต่กำลังกลายเป็นผลิตภัณฑ์เชิงพาณิชย์จริง
เบื้องหลังของโปรเจกต์นี้คือการลงทุนกว่า 30 ล้านดอลลาร์สหรัฐจากกลุ่มทุนทั่วโลก รวมถึงบริษัท Solar Biotech ที่จับมือกับ TurtleTree ในการขยายกำลังการผลิตเชิงอุตสาหกรรมในสหรัฐอเมริกา โดยตั้งเป้าว่าจะสามารถผลิตโปรตีนเหล่านี้ได้ในระดับราคาที่แข่งขันได้ภายในไม่กี่ปีข้างหน้า
สิ่งที่น่าสนใจคือ TurtleTree ไม่ได้หยุดแค่ lactoferrin พวกเขายังวางแผนพัฒนา HMO ซึ่งเป็นน้ำตาลเชิงซ้อนชนิดพิเศษที่มีอยู่เฉพาะในน้ำนมแม่ เป็นอาหารเลี้ยงแบคทีเรียดีในลำไส้ทารก ช่วยพัฒนาระบบภูมิคุ้มกันและสมอง ปัจจุบัน HMOs เริ่มเป็นที่นิยมในวงการ infant formula แต่การผลิตยังจำกัดและมีต้นทุนสูง การที่ TurtleTree จะนำเทคโนโลยี precision fermentation มาใช้ผลิต HMO จึงถือเป็นความพยายามในการลดช่องว่างระหว่าง "นมแม่จริง" กับ "นมผงสังเคราะห์"
ทั้งหมดนี้เกิดขึ้นภายใต้แนวคิดใหม่ของอุตสาหกรรมอาหารที่เรียกว่า "functional nutrition" หรือโภชนาการที่ออกแบบเพื่อทำงานเฉพาะทาง ไม่ใช่แค่ให้พลังงานหรือโปรตีน แต่เล็งเป้าหมายเฉพาะ เช่น เสริมภูมิคุ้มกัน ซ่อมแซมสมอง หรือฟื้นฟูร่างกาย โดยมีรากฐานจากธรรมชาติ แต่ใช้เทคโนโลยีสมัยใหม่ในการผลิต
แม้จะฟังดูเป็นความก้าวหน้าทางวิทยาศาสตร์ที่น่าตื่นเต้น แต่น้ำเสียงที่ดังก้องในอีกมุมหนึ่งก็คือคำถามเชิงจริยธรรม TurtleTree กำลังสร้างโปรตีนที่มีอยู่เฉพาะในมนุษย์ โดยอาศัยข้อมูลพันธุกรรมของมนุษย์เอง แล้วนำเข้าสู่ระบบอุตสาหกรรมเพื่อการค้า คำถามคือ เมื่อใดที่การจำลองธรรมชาติจะกลายเป็นการผูกขาดธรรมชาติ? ใครควรเป็นเจ้าของข้อมูลพันธุกรรมของมนุษย์? และถ้าวันหนึ่งบริษัทใดบริษัทหนึ่งสามารถควบคุมการผลิต “นมแม่จำลอง” ได้แต่เพียงผู้เดียว นั่นจะส่งผลต่อเสรีภาพของสังคมในมุมไหนบ้าง?
นักชีวจริยธรรมหลายคน เช่น ดร.ซิลเวีย แคมโปเรซี จาก King's College London ตั้งข้อสังเกตไว้ว่า เทคโนโลยีแบบนี้อาจแก้ปัญหาการเข้าถึงนมแม่ในพื้นที่ห่างไกลหรือในกลุ่มแม่ที่ให้นมไม่ได้ แต่ขณะเดียวกันก็อาจกลายเป็นการสร้าง "ระบบอาหารทางเลือก" ที่ควบคุมโดยบริษัทไม่กี่ราย ที่มีอำนาจเกินกว่าผู้บริโภคจะตรวจสอบได้
เมื่อเทคโนโลยีสามารถจำลองสิ่งที่เคยสงวนไว้เฉพาะธรรมชาติ และมนุษย์ได้ใกล้เคียงจนแทบแยกไม่ออก บางทีคำถามที่ควรถามอาจไม่ใช่แค่ว่า “มันปลอดภัยหรือไม่?” แต่อาจต้องถามว่า “เราไว้ใจใครให้สร้างสิ่งนี้แทนธรรมชาติ?” เพราะน้ำนมแม่เคยเป็นสิ่งที่มาจากรักและชีวิต แต่วันนี้มันอาจกลายเป็นเพียงสิ่งที่มาจากห้องแล็บและโมเลกุล... และนั่นคือสิ่งที่เราต้องคิดให้เป็น ก่อนจะกินให้ดี เต่านี้มีบุญคุณอันใหญ่หลวงงงงงงง
เสริมจุดน่าสนใจให้ครับ KBW Ventures ถือเป็นผู้ลงทุนรายใหญ่ที่สุดใน TurtleTree Labs โดยมีบทบาทสำคัญในหลายรอบการระดมทุนของบริษัท KBW Ventures เป็นบริษัทลงทุนจากสหรัฐอาหรับเอมิเรตส์ ก่อตั้งโดย สมเด็จพระราชโอรสเจ้าชายคาเล็ด บิน อัลวาลีด บิน ตาลาล อัล ซาอุด (HRH Prince Khaled bin Alwaleed bin Talal Al Saud) ในรอบการระดมทุน Pre-A มูลค่า 6.2 ล้านดอลลาร์สหรัฐฯ ซึ่งปิดในเดือนธันวาคม 2020 KBW Ventures ได้ร่วมลงทุนพร้อมกับ Green Monday Ventures, Eat Beyond Global และ Verso Capital . นอกจากนี้ เจ้าชาย Khaled ยังได้เข้าร่วมเป็นที่ปรึกษาให้กับ TurtleTree Labs เพื่อสนับสนุนการขยายตลาดและกลยุทธ์การเติบโตของบริษัท
ซึ่งในตัว KBW Ventures นั้น เป็นบริษัทลงทุนที่มุ่งเน้นการสนับสนุนเทคโนโลยีที่ยั่งยืนและนวัตกรรมในหลากหลายอุตสาหกรรม เช่น เทคโนโลยีชีวภาพ (biotech), เทคโนโลยีพลังงานสะอาด, เทคโนโลยีการเงิน (fintech), เทคโนโลยีการขนส่ง, และเทคโนโลยีอาหาร (food tech) โดยเฉพาะ และในส่วนของเจ้าชาย Khaled มีความสนใจอย่างลึกซึ้งในด้านเทคโนโลยีอาหาร โดยเฉพาะในกลุ่มโปรตีนทางเลือก เช่น Beyond Meat ซึ่งเป็นการลงทุนที่สะท้อนถึงความมุ่งมั่นชัดเจนในการส่งเสริมอาหารที่ยั่งยืนและมีจริยธรรมครับ และแน่นอนเลยว่า โดยมีส่วนร่วมในรอบระดมทุนหลายครั้งของ Beyond Meat รวมถึงตอนที่ Beyond Meat เข้าตลาดหุ้น Nasdaq ครั้งแรกในปี 2019
เจ้าชาย Khaled เชื่อมั่นว่าอาหารทางเลือกแบบพืชจะถูกลงและแพร่หลายมากขึ้น จนอาจถูกกว่าราคาเนื้อสัตว์จากสัตว์จริงภายในปี 2025 ตามข้อมูลที่ได้มาแสดงว่า ปีนี้นี่หว่าาาาาาาาาา
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 04c915da:3dfbecc9
2025-05-16 17:51:54
@ 04c915da:3dfbecc9
2025-05-16 17:51:54In much of the world, it is incredibly difficult to access U.S. dollars. Local currencies are often poorly managed and riddled with corruption. Billions of people demand a more reliable alternative. While the dollar has its own issues of corruption and mismanagement, it is widely regarded as superior to the fiat currencies it competes with globally. As a result, Tether has found massive success providing low cost, low friction access to dollars. Tether claims 400 million total users, is on track to add 200 million more this year, processes 8.1 million transactions daily, and facilitates $29 billion in daily transfers. Furthermore, their estimates suggest nearly 40% of users rely on it as a savings tool rather than just a transactional currency.
Tether’s rise has made the company a financial juggernaut. Last year alone, Tether raked in over $13 billion in profit, with a lean team of less than 100 employees. Their business model is elegantly simple: hold U.S. Treasuries and collect the interest. With over $113 billion in Treasuries, Tether has turned a straightforward concept into a profit machine.
Tether’s success has resulted in many competitors eager to claim a piece of the pie. This has triggered a massive venture capital grift cycle in USD tokens, with countless projects vying to dethrone Tether. Due to Tether’s entrenched network effect, these challengers face an uphill battle with little realistic chance of success. Most educated participants in the space likely recognize this reality but seem content to perpetuate the grift, hoping to cash out by dumping their equity positions on unsuspecting buyers before they realize the reality of the situation.
Historically, Tether’s greatest vulnerability has been U.S. government intervention. For over a decade, the company operated offshore with few allies in the U.S. establishment, making it a major target for regulatory action. That dynamic has shifted recently and Tether has seized the opportunity. By actively courting U.S. government support, Tether has fortified their position. This strategic move will likely cement their status as the dominant USD token for years to come.
While undeniably a great tool for the millions of users that rely on it, Tether is not without flaws. As a centralized, trusted third party, it holds the power to freeze or seize funds at its discretion. Corporate mismanagement or deliberate malpractice could also lead to massive losses at scale. In their goal of mitigating regulatory risk, Tether has deepened ties with law enforcement, mirroring some of the concerns of potential central bank digital currencies. In practice, Tether operates as a corporate CBDC alternative, collaborating with authorities to surveil and seize funds. The company proudly touts partnerships with leading surveillance firms and its own data reveals cooperation in over 1,000 law enforcement cases, with more than $2.5 billion in funds frozen.
The global demand for Tether is undeniable and the company’s profitability reflects its unrivaled success. Tether is owned and operated by bitcoiners and will likely continue to push forward strategic goals that help the movement as a whole. Recent efforts to mitigate the threat of U.S. government enforcement will likely solidify their network effect and stifle meaningful adoption of rival USD tokens or CBDCs. Yet, for all their achievements, Tether is simply a worse form of money than bitcoin. Tether requires trust in a centralized entity, while bitcoin can be saved or spent without permission. Furthermore, Tether is tied to the value of the US Dollar which is designed to lose purchasing power over time, while bitcoin, as a truly scarce asset, is designed to increase in purchasing power with adoption. As people awaken to the risks of Tether’s control, and the benefits bitcoin provides, bitcoin adoption will likely surpass it.
-
 @ 502ab02a:a2860397
2025-05-22 01:30:37
@ 502ab02a:a2860397
2025-05-22 01:30:37ถ้าพูดถึง "เกาหลีใต้" หลายคนอาจนึกถึงซีรีส์ น้ำจิ้มเผ็ด หรือไอดอลหน้าผ่อง ๆ แต่เบื้องหลังวัฒนธรรมที่ลื่นไหลไปทั่วโลกนี้ ยังมีอาณาจักรธุรกิจขนาดมหึมาที่เป็นเหมือนเครื่องยนต์หลักผลักดันทั้งอาหาร เพลง หนัง และนวัตกรรมระดับโลก หนึ่งในนั้นคือ CJ Group ที่เริ่มต้นจากบริษัทน้ำตาลเล็ก ๆ ในปี 1953 แต่เติบโตจนกลายเป็นหนึ่งใน conglomerate หรือ "กลุ่มธุรกิจผูกเครือ" ที่ทรงอิทธิพลที่สุดของแดนโสม
คำว่า CJ ย่อมาจาก CheilJedang (แปลว่า “หมายเลขหนึ่งแห่งโลก” ในภาษาจีน-เกาหลี) ก่อตั้งโดย อี บยองชอล ผู้ก่อตั้ง Samsung Group ในช่วงเวลานั้น เกาหลีใต้กำลังฟื้นตัวจากสงครามเกาหลี และรัฐบาลส่งเสริมการพัฒนาอุตสาหกรรมภายในประเทศ เดิมเป็นหน่วยธุรกิจอาหารของกลุ่ม Samsung ในปี 1993 Cheil Jedang แยกตัวออกจาก Samsung Group และกลายเป็นบริษัทอิสระภายใต้การบริหารของ อี แจฮยอน หลานชายของอี บยองชอล แล้วขยายขอบเขตธุรกิจอย่างไม่หยุดยั้ง จากความเชี่ยวชาญใน "การหมัก" แบบดั้งเดิม พวกเขากลับกลายเป็นผู้เล่นรายใหญ่ระดับโลกในวงการ เทคโนโลยีชีวภาพ การผลิตอาหารไปจนถึงธุรกิจ บันเทิงระดับฮอลลีวูด และ โลจิสติกส์ข้ามทวีป
พูดง่าย ๆ ว่า CJ ไม่ได้แค่ส่งออกกิมจิหรือบิบิมบับ แต่พวกเขากำลังวางรากฐานของ "อนาคตแห่งอาหาร" และ "ความบันเทิงแบบไร้พรมแดน" ในเวลาเดียวกัน จนใครหลายคนถึงกับบอกว่า ถ้าอยากเข้าใจเกาหลีใต้ ก็ต้องเริ่มจากเข้าใจ CJ Group เสียก่อน
แล้วในเครือข่ายของ CJ Group มีธุรกิจอะไรบ้างที่น่าสนใจ และแบรนด์ไหนที่เราคุ้นเคยแบบไม่รู้ตัว ไปดูกันเลย
- ธุรกิจอาหารและบริการอาหาร (Food & Food Services)
- CJ CheilJedang บริษัทอาหารชั้นนำของเกาหลีใต้ มีผลิตภัณฑ์เด่น ได้แก่ Bibigo แบรนด์อาหารเกาหลีพร้อมรับประทาน เช่น เกี๊ยว ซอส และกิมจิ Hetbahn ข้าวสวยพร้อมรับประทานที่ได้รับความนิยมในเกาหลี
-
CJ Foodville ดำเนินธุรกิจร้านอาหารและเบเกอรี่ เช่น: Tous Les Jours ร้านเบเกอรี่สไตล์ฝรั่งเศส VIPS ร้านสเต็กและสลัดบุฟเฟ่ต์
-
ธุรกิจเทคโนโลยีชีวภาพ (Bio) ความเชี่ยวชาญนี้เป็นรากฐานสำคัญในการขยายธุรกิจด้านเทคโนโลยีชีวภาพของ CJ เลยครับ
- CJ BIO ผู้นำด้านการผลิตกรดอะมิโนและผลิตภัณฑ์ชีวภาพผ่านเทคโนโลยีการหมักจุลินทรีย์ เช่น Lysine, Tryptophan, Valine กรดอะมิโนที่ใช้ในอุตสาหกรรมอาหารสัตว์และอาหารเสริม
-
CJ Bioscience มุ่งเน้นการวิจัยและพัฒนาไมโครไบโอมเพื่อสุขภาพ
-
ธุรกิจโลจิสติกส์และค้าปลีก (Logistics & Retail)
- CJ Logistics ให้บริการโลจิสติกส์ครบวงจร ทั้งการขนส่งทางบก ทางทะเล และทางอากาศ รวมถึงบริการคลังสินค้าและการจัดการซัพพลายเชน
-
CJ Olive Young: ร้านค้าปลีกด้านสุขภาพและความงามอันดับหนึ่งของเกาหลี มีผลิตภัณฑ์ยอดนิยม เช่น Anua PDRN Set ชุดบำรุงผิวที่ได้รับความนิยม MILKTOUCH ผลิตภัณฑ์เมคอัพที่ได้รับความนิยม
-
ธุรกิจบันเทิงและสื่อ (Entertainment & Media) อันนี้ยิ่งใหญ่ระดับโลกมากๆ หลายคนคงจำได้กับ ภาพยนตร์เอเชียแรกกับรางวัลออสการ์ Parasite
- CJ ENM บริษัทผลิตและจัดจำหน่ายเนื้อหาบันเทิงที่มีชื่อเสียงระดับโลก มีผลงานเด่น ได้แก่ Crash Landing on You ซีรีส์ที่ได้รับความนิยมอย่างสูง Parasite ภาพยนตร์ที่ได้รับรางวัลออสการ์
- CJ CGV เครือโรงภาพยนตร์มัลติเพล็กซ์ที่มีสาขาทั่วโลก
CJ Group ขยายธุรกิจไปยังต่างประเทศ เช่น การเข้าซื้อกิจการ Schwan's Company ในสหรัฐอเมริกา และการเปิดสาขา CGV ในหลายประเทศ นอกจากนี้ CJ ยังมีบทบาทสำคัญในการเผยแพร่วัฒนธรรมเกาหลีสู่ระดับโลกผ่าน KCON และการผลิตเนื้อหาบันเทิงที่ได้รับความนิยมในต่างประเทศด้วยครับ
จะเห็นได้ว่า เครือข่ายของ CJ นั้นยิ่งใหญ่มากๆเลย ทีนี้มีเรื่องน่าสนใจตรงนี้ครับ
ในช่วงปี 2013–2016 CJ Group โดยเฉพาะฝ่ายสื่อบันเทิงอย่าง CJ ENM ต้องเผชิญกับแรงกดดันจากรัฐบาลของประธานาธิบดี พัค กึนฮเย เหตุการณ์สำคัญคือการที่ อี มีคยอง (Miky Lee) รองประธาน CJ และผู้มีบทบาทสำคัญในการขับเคลื่อนธุรกิจบันเทิงระดับโลก ถูกกดดันให้ลาออกจากตำแหน่ง รายงานระบุว่า ทำเนียบประธานาธิบดีไม่พอใจเนื้อหาสื่อบางรายการของ CJ ที่มีลักษณะเสียดสีหรือวิพากษ์วิจารณ์รัฐบาล เช่น รายการ SNL Korea ที่ล้อเลียนพัค กึนฮเย ผ่านตัวละคร Teletubbies
ภายใต้แรงกดดันนี้ CJ มีการปรับเปลี่ยนเนื้อหาสื่อ โดยลดการนำเสนอเนื้อหาที่อาจขัดแย้งกับรัฐบาล และหันไปผลิตภาพยนตร์ที่สอดคล้องกับนโยบายของรัฐ เช่น ภาพยนตร์เรื่อง Ode to My Father (2014) ที่สะท้อนความรักชาติและการพัฒนาเศรษฐกิจในยุคของพัค ชุงฮี บิดาของพัค กึนฮเย ภาพยนตร์เรื่องนี้ได้รับการสนับสนุนจากรัฐบาลและถูกมองว่าเป็น "ภาพยนตร์เพื่อสุขภาพ" ที่ส่งเสริมความภาคภูมิใจในชาติ แน่นอนว่าแค้นฝังหุ่นมันยังไม่หายไปไหนครับ
เมื่อเกิดการเปิดโปง "บัญชีดำ" (Blacklist) ของรัฐบาลพัค กึนฮเย ที่มีการจำกัดสิทธิเสรีภาพของศิลปินและผู้ผลิตสื่อที่วิพากษ์วิจารณ์รัฐบาล ทำให้เกิดกระแสต่อต้านอย่างรุนแรงในสังคมเกาหลี. ในปี 2016 ซน กยองชิก ประธาน CJ ได้ให้การต่อศาลว่า มีแรงกดดันจากรัฐบาลให้ อี มีคยอง หลีกเลี่ยงการมีบทบาทในบริษัท เหตุการณ์นี้เป็นส่วนหนึ่งของการเปิดโปงคดีทุจริตของพัค กึนฮเย ซึ่งนำไปสู่การประท้วงครั้งใหญ่และการถอดถอนประธานาธิบดีในปี 2017
หลังจากการเปลี่ยนแปลงทางการเมือง CJ Group ได้กลับมามีบทบาทอย่างเต็มที่ในวงการบันเทิงอีกครั้ง อี มีคยอง กลับมาดำรงตำแหน่งและมีบทบาทสำคัญในการผลักดันภาพยนตร์เรื่อง Parasite (2019) ซึ่งได้รับรางวัลออสการ์และยกระดับภาพลักษณ์ของ CJ ในระดับโลก ซึ่งถ้าใครได้ดูหนังเรื่องนั้นแล้วรู้เรื่องราวเบื้องหลังนี้จะเข้าใจเนื้อหาได้อย่างลึกซึ้งขึ้นไปอีกเลยครับ การนำเสนอเรื่องราวนี้ถือเป็นการวิพากษ์วิจารณ์สังคมและระบบทุนนิยมอย่างชัดเจน ซึ่งแตกต่างจากแนวทางที่ CJ เคยถูกกดดันให้ปฏิบัติตามในยุคของพัค กึนฮเย อย่างสิ้นเชิง
อย่าเพิ่งไปสะใจกับเนื้อหา ให้มองว่า "เขาทำอะไรได้บ้าง" นี่คือประเด็นสำคัญครับ #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 04c915da:3dfbecc9
2025-03-10 23:31:30
@ 04c915da:3dfbecc9
2025-03-10 23:31:30Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Usually stolen bitcoin for the reserve creates a perverse incentive. If governments see a bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ eed76ece:afa98124
2024-08-13 18:50:40
@ eed76ece:afa98124
2024-08-13 18:50:40Hopefully people out there that are importers, exporters, agents, traders, wholesalers in various types of goods, will eventually post, or at the very least find some possible business leads, contacts and most importantly reviews on payments methods using Bitcoin around the World.
The Good News
-
Wholesale and Retail merchants have heard the Independent, Democratic and Republican parties are speaking in a positive tone about Bitcoin and the C word in general. Whether any of them actually will do anything in the future is another issue, note the fact that Bitcoin and the C word is being brought up in a positive way is a good.
-
Bitcoin Dev groups are opening up in more places around the World and obviously some general education, terminology and introduction to Lightning, Nostr, and hybrid point of sale systems are slowly be added to merchants retail and wholesale.
-
Shopify, As the majority of business are using Shopify, Open Node is easily added as a payment method to accept Bitcoin. (I'm using it) works fine, had to as ibexpay left supporting the USA.
-
"Just hodl" comes up more and more in conversations with my peers, asking with a confused look "When do we use it, circulate it in transacting buying or selling goods (wholesale), NOT just a cup of coffee, we are just suppose to hodl, and never use it ?
-
We have SN, we should be thankful it's a positive tool.
If anyone wants to communicate with other manufacturers, wholesalers, B2B merchants, importers, exporters, agents selling goods of any type consider reaching out as a post on SN, or contacting me directly, hopefully that you are considering using Bitcoin as the payment method.
Stay humble use SATS
originally posted at https://stacker.news/items/647600
-
-
 @ 8f69ac99:4f92f5fd
2025-04-07 15:35:08
@ 8f69ac99:4f92f5fd
2025-04-07 15:35:08No dia 2 de Abril de 2025, o Presidente dos Estados Unidos, Donald Trump, anunciou um novo pacote abrangente de tarifas com o objectivo de combater os desequilíbrios comerciais e revitalizar as indústrias nacionais. Foi imposta uma tarifa geral de 10% sobre todas as importações, com taxas mais elevadas—34% para a China e 20% para a União Europeia—em preparação para entrar em vigor. O anúncio reacendeu debates antigos sobre proteccionismo, globalização e o futuro do dólar norte-americano.
Embora estas medidas possam parecer extremas, as tarifas são um instrumento tradicional da política comercial internacional. Países de todo o mundo, incluindo a União Europeia, utilizam-nas rotineiramente para proteger indústrias estratégicas, regular o comércio e gerar receitas. A UE, por exemplo, impõe há muito tempo taxas sobre produtos norte-americanos como bens agrícolas, maquinaria e têxteis. Em contrapartida, os EUA já taxaram importações da UE, como o aço, alumínio e aeronaves, em disputas comerciais.
O que distingue a proposta de Trump é a sua escala, ambição e o objectivo mais amplo: reestruturar a economia dos EUA. Por detrás desta estratégia está uma realidade económica mais profunda—moldada por décadas de défices comerciais, endividamento crescente e o papel do dólar como moeda de reserva mundial. Este artigo explora como estes factores se cruzam, por que razão os EUA se encontram numa posição precária, e se políticas como tarifas elevadas, taxas de juro baixas ou até o Bitcoin podem apontar o caminho a seguir.
As Raízes da Crise: Sobreconsumo e Desindustrialização nos EUA
Durante décadas, os Estados Unidos "viveram acima das suas possibilidades", acumulando um défice comercial que actualmente ultrapassa os 800 mil milhões de dólares por ano. Este desequilíbrio—em que o país compra mais do que vende ao exterior—é sintoma de um problema mais profundo. No pós-Segunda Guerra Mundial, os EUA eram uma potência industrial. Mas, a partir dos anos 70, e com maior intensidade nos anos 90, a globalização transferiu a produção para o estrangeiro. As empresas procuraram custos de mão de obra mais baixos e os mercados norte-americanos encheram-se de produtos fabricados fora.
Para sustentar este consumo, os EUA apoiaram-se na sua posição privilegiada: a emissão da moeda de reserva mundial. Isso gerou um ciclo de endividamento, com o país a pedir emprestado ao exterior para manter o nível de vida. O resultado? Desindustrialização. Fábricas fecharam e milhões de empregos na indústria desapareceram em estados como Ohio, Michigan e Pensilvânia.
Hoje, os EUA produzem muito menos—em proporção ao seu tamanho—do que há algumas décadas, mesmo mantendo um apetite crescente por importações. O défice comercial expõe uma fragilidade estrutural: um país cada vez mais incapaz de sustentar-se através da sua própria produção. Os dólares gastos fora regressam muitas vezes sob a forma de compras de dívida pública, perpetuando o ciclo.
À medida que os défices crescem e a economia depende cada vez mais de mecanismos financeiros do que da produção real, surge uma questão inevitável: até quando poderá a América continuar a comprar a crédito antes que o cartão seja recusado?
O Dilema de Triffin: Moeda Global vs. Potência Industrial
Imagine ser a única pessoa numa cidade com uma impressora de dinheiro que todos usam. Para satisfazer a procura, continua a imprimir e a enviar notas para o exterior—até que o seu próprio negócio local entra em decadência e se torna dependente dos outros. Esta é a essência do Dilema de Triffin, e a corda bamba que os EUA têm vindo a atravessar há gerações.
O dilema surge quando a moeda de um país é usada como padrão global. O dólar—utilizado mundialmente para transacções de petróleo, comércio e reservas—precisa de estar amplamente disponível. Essa abundância provém de défices comerciais persistentes por parte dos EUA.
Mas os défices têm um custo. Os dólares enviados para fora voltam como procura por bens estrangeiros, enfraquecendo a produção interna. Porque fabricar um produto em Detroit por 10 dólares, quando se pode importar por $2? Com o tempo, isto destrói a base industrial do país.
Esta não é uma preocupação teórica—é uma realidade histórica. O economista Robert Triffin advertiu nos anos 60 que um país não pode simultaneamente manter a sua moeda como padrão mundial e conservar uma base industrial sólida. Os EUA confirmaram essa previsão. Após a guerra, os dólares ajudaram a reconstruir a Europa e o Japão, mas esses mesmos países tornaram-se concorrentes industriais dos EUA em sectores como o aço e a indústria automóvel.
As fábricas abandonadas no Midwest e os teares silenciosos no sul são marcas visíveis desta troca. O domínio do dólar concedeu influência global à América, mas às custas da sua produção.
Espiral da Dívida: Obrigações Financeiras Crescentes dos EUA
Em 2025, a dívida federal dos EUA ultrapassa os 36 biliões de dólares ($36 000 000 000 000 000 000)—cerca de 108 mil dólares por cada americano, adultos, jovens, idosos. Durante anos, o acesso fácil ao crédito e a procura global por dívida americana mascararam os riscos. Agora, as fissuras estão à vista.
O problema não é apenas o montante—é o prazo e o custo de manter esta dívida. Grande parte dela é de curto prazo, exigindo refinanciamentos frequentes. Com o aumento das taxas de juro, os custos associados disparam. Só em 2024, os pagamentos de juros ultrapassaram 1 bilião de dólares—mais do que os orçamentos combinados de educação, transportes e habitação.
A “Lei de Ferguson”, proposta pelo historiador Niall Ferguson, afirma que quando os juros da dívida superam os gastos militares, o império está em declínio. Em 2025, os EUA gastam cerca de 900 mil milhões em defesa, e os encargos com juros já os ultrapassaram.
Este ponto de viragem trouxe problemas a impérios do passado—do Reino Unido após a Primeira Guerra Mundial até Roma no seu declínio. Hoje, cresce o cepticismo quanto à saúde fiscal dos EUA. Países como a China e a Rússia estão a reduzir as suas reservas em dívida americana, preferindo ouro, yuan ou outros activos.
Se mais nações seguirem o mesmo caminho, os EUA terão de escolher: continuar a endividar-se para sustentar o sistema ou aceitar um papel reduzido para o dólar na economia mundial.
Desdolarização: A Mudança Global Longe do Dólar
A desdolarização refere-se à tendência crescente de reduzir a dependência do dólar nas transacções comerciais, reservas e sistemas financeiros. Embora o dólar ainda domine, a sua supremacia está sob crescente pressão de novas potências económicas e tensões geopolíticas.
Porque Está o Mundo a Afastar-se do Dólar?
- Risco Económico: A volatilidade do dólar, agravada pela dívida e instabilidade política nos EUA, torna-o menos fiável como reserva de valor.
- Instrumento Geopolítico: O uso do dólar pelos EUA para impor sanções leva rivais a procurar alternativas.
Alternativas Emergentes
- Ouro: Bancos centrais estão a reforçar as reservas em ouro como protecção.
- Commodities: Petróleo e cereais começam a ser transaccionados em moedas alternativas—como vendas de petróleo em yuan pela Arábia Saudita.
- Criptomoedas: Bitcoin e outros activos digitais ganham terreno como reservas neutras e descentralizadas.
- Moedas Regionais: Os países dos BRICS desenvolvem sistemas de pagamento e discutem uma moeda comum para reduzir a dependência do dólar.
Um Declínio Lento, Mas Visível
A percentagem do dólar nas reservas cambiais mundiais caiu de 70% no ano 2000 para menos de 60% actualmente. O comércio em moedas não-dólar cresceu 25% desde 2020. O domínio do dólar persiste, mas o movimento de mudança é claro.
A Estratégia Económica de Trump em 3 Etapas
Em 2025, Trump apresentou uma estratégia económica audaciosa em três frentes:
1. Tarifas Elevadas para Revitalizar a Indústria
Uma tarifa de 10% sobre todas as importações, com taxas superiores para países com superavit comercial, visa incentivar a produção interna. Críticos alertam para o aumento de preços e inflação, mas apoiantes defendem que é necessário para reindustrializar.
2. Redução das Taxas de Juro para Gerir a Dívida
A administração pressiona a Reserva Federal para baixar as taxas, reduzindo os encargos da dívida pública. Isto levanta preocupações sobre a independência do banco central e a estabilidade monetária a longo prazo.
3. Bitcoin como Activo Estratégico de Reserva
Num passo histórico, Trump assinou uma ordem executiva para criar a Reserva Estratégica de Bitcoin e o Stock Nacional de Activos Digitais. O objectivo é diversificar as reservas e proteger contra a inflação.
Riscos e Compensações
A estratégia económica de Trump não está isenta de riscos:
- Inflação: Tarifas mais altas poderão aumentar o custo de vida.
- Polarização Política: Medidas controversas poderão acentuar divisões internas.
- Incerteza Económica: O proteccionismo pode afastar investimento e travar a inovação.
- Instabilidade Monetária: Um erro na gestão da dívida ou dos activos digitais poderá enfraquecer o dólar.
Estes riscos exigem gestão cuidadosa para evitar agravar os problemas existentes.
O Papel de Bitcoin: Protecção ou Último Recurso?
Integrar Bitcoin nas reservas nacionais é ousado—mas pode ser revolucionário, e a meu ver, inevitável!
Vantagens
- Escassez: Com oferta limitada a 21 milhões de unidades, Bitcoin é deflacionário.
- Descentralização: Resistente à censura e manipulação, reforça a soberania financeira.
- Alcance Global: Sem fronteiras, permite trocas neutras num mundo multipolar.
Desafios
- Volatilidade: As flutuações no curto prazo são ainda significativas, mas a adopção institucional pode estabilizar o preço.
- Regulação: O enquadramento legal está em evolução, mas tende para maior clareza.
- Adopção Técnica: Persistem desafios de escalabilidade, embora soluções como a Lightning Network estejam a amadurecer.
A Reserva Estratégica de Bitcoin pode revelar-se visionária—ou precipitada. Tudo dependerá da execução e da aceitação global.
Futuros Possíveis: Crise ou Reinvenção?
Os EUA estão perante uma encruzilhada histórica. Um caminho aponta para a renovação: revitalizar a indústria e adoptar activos digitais, como por exemplo as stablecoins para perpetuar a hegemonia do dólar, lastreado em Bitcoin. O outro conduz à crise—com inflação, instabilidade e perda de influência global.
Num cenário optimista, os EUA emergem como líderes industriais e digitais, com reservas diversificadas que incluem Bitcoin. A recente ordem executiva para adquirir Bitcoin de forma neutra ao orçamento é um sinal positivo.
Num cenário pessimista, menos provável com as medidas em curso, o país mergulha em dívidas, vê o dólar enfraquecer e perde coesão interna. Mas com visão estratégica e inovação económica, há margem para navegar os desafios com sucesso.
Conclusão
A América enfrenta uma oportunidade única de redefinir o seu destino económico. A estratégia de Trump—baseada em tarifas, taxas de juro baixas e Bitcoin—pode marcar o início de uma nova era de resiliência e recuperação industrial.
A inclusão de Bitcoin nas reservas nacionais mostra que os instrumentos tradicionais já não bastam. Ao abraçar os activos digitais e restaurar a produção nacional, os EUA podem recuperar a liderança económica mundial.
O caminho será difícil. Mas com ousadia e execução eficaz, os Estados Unidos não só podem recuperar—podem reinventar-se.
-
 @ 04c915da:3dfbecc9
2025-03-07 00:26:37
@ 04c915da:3dfbecc9
2025-03-07 00:26:37There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ 502ab02a:a2860397
2025-05-21 07:49:22
@ 502ab02a:a2860397
2025-05-21 07:49:22หลายคนอาจแปลกใจว่า ทำไมน้ำมันจากผลไม้แบบอโวคาโดถึงกล้าขึ้นชั้น “ไขมันดี” ไปเทียบกับน้ำมันมะกอกได้ ทั้งที่ฟังดูไม่หรูเท่า แต่ความจริงแล้ว น้ำมันอโวคาโดคือหนึ่งในไม่กี่ชนิดของน้ำมันพืชที่สกัดจาก “เนื้อผล” ไม่ใช่เมล็ด ทำให้มีโครงสร้างไขมันที่ต่างจาก seed oils ทั่วไป ทั้งในแง่กรดไขมัน สารต้านอนุมูลอิสระ และวิธีที่มันตอบสนองต่อความร้อน
น้ำมันอโวคาโดมีกรดไขมันไม่อิ่มตัวตำแหน่งเดียว (MUFA) เป็นหลัก โดยเฉพาะ กรดโอเลอิก (Oleic acid) ซึ่งคิดเป็นประมาณ 65–70% ของไขมันทั้งหมด ใกล้เคียงน้ำมันมะกอกเลย แต่เหนือกว่าเล็กน้อยในแง่ของ ค่าควัน (smoke point) ที่สูงถึง 250°C (แบบ refined) และราว 190–200°C (แบบ cold-pressed) ทำให้เหมาะกับการผัดหรือทอดแบบเบา ๆ โดยไม่ทำให้เกิดสารพิษจากไขมันไหม้เร็วเท่าน้ำมันที่ค่าควันต่ำ
นอกจาก MUFA แล้ว น้ำมันอโวคาโดยังมี PUFA อยู่เล็กน้อย ประมาณ 10–14% ส่วนใหญ่คือ โอเมก้า-6 (linoleic acid) ซึ่งก็มีปริมาณไม่มากจนถึงขั้นต้องห่วงเรื่องการอักเสบ เหมือนที่เจอกับพวกน้ำมันรำข้าวหรือถั่วเหลืองที่ PUFA พุ่งสูงเกิน 50% ขึ้นไป และที่สำคัญ...โอเมก้า-3 ในอโวคาโดก็มีอยู่บ้างในรูปของ ALA แม้ไม่เยอะ แต่ก็บอกได้ว่าโครงสร้างโดยรวมของมันสมดุลพอควร ถ้ามองในรูปแบบพลังงานไขมัน ก็ถือว่าใช้ได้เลย
อโวคาโดออยล์แบบไม่ผ่านกระบวนการ (unrefined) ยังมีพวก วิตามินอี (tocopherols) ในระดับประมาณ 13–20 มก. ต่อ 100 กรัม และสารโพลีฟีนอลบางชนิดราวๆ 30–50 mg GAE/100 กรัม เช่น catechins และ procyanidins อยู่บ้าง ซึ่งช่วยลดการเกิดอนุมูลอิสระตอนเจอความร้อน และยังดีต่อผิวหนังในมิติของ skincare ด้วยนะ
ถ้าใช้แบบ cold-pressed, unrefined กลิ่นมันจะออกคล้ายอะโวคาโดสุก ๆ หน่อย มีความเขียวอ่อน ๆ และครีมมี่เล็ก ๆ ซึ่งเหมาะกับการคลุกหรือปรุงแบบ low heat มากกว่าการทอดแรง ส่วนถ้าจะใช้ทำอาหารจริงจัง น้ำมันอโวคาโดแบบ refined ก็จะกลิ่นอ่อนลง สีใสขึ้น และทนไฟได้ดีขึ้นมาก เหมาะจะเอาไปทำ steak หรือผัดไฟกลางได้แบบไม่กังวล อันนี้ก็แล้วแต่จะเลือกนะครับ
ถ้าจะพูดให้ตรง… น้ำมันอโวคาโดคือ “ไขมันผลไม้สายกลาง” ที่ทั้งทนไฟพอใช้ ทำครัวได้หลากหลาย และไม่บิดเบือนสัดส่วนไขมันในร่างกายเราจนเกินไป และถ้าเลือกแบบที่ผลิตดี ไม่โดนสารเคมี ไม่โดนไฮโดรเจนเสริม ก็ถือว่าเป็นน้ำมันดีอีกตัวที่วางใจได้ในครัวจริง ๆ
ใครอยากลองทำเองที่บ้านก็ได้นะ แบบง่ายๆแค่มีผ้าขาวบาง https://youtu.be/gwHGgoMuRnI?si=ehcQceabdbMGfkwG
นอกจากนี้บางคนอาจเคยเห็นโฆษณาสินค้าที่มีน้ำมันจากเมล็ดและเปลือกด้วยใช่ไหมครับ
เมล็ดอโวคาโดนั้นอุดมไปด้วย ไขมันน้อยกว่ามาก เมื่อเทียบกับเนื้อผล แต่มีสารพฤกษเคมีบางชนิดที่นักวิจัยสนใจ เช่น ฟีนอลิกส์ (phenolics), ฟลาโวนอยด์, สารต้านจุลชีพ และ ไฟเบอร์ละลายน้ำสูง การสกัดน้ำมันจากเมล็ดมักจะใช้ ตัวทำละลาย (solvent extraction) หรือ วิธี supercritical CO₂ ไม่ค่อยทำแบบ cold-pressed เพราะน้ำมันน้อยเกิน ปริมาณน้ำมันจากเมล็ดนั้นต่ำมาก คือไม่ถึง 5% ของน้ำหนักแห้ง ทำให้ไม่ค่อยนิยมในเชิงพาณิชย์ น้ำมันจากเมล็ดมักไม่ได้เอาไว้ปรุงอาหาร แต่เอาไปใช้ ด้านเวชสำอาง หรือ functional food มากกว่า เช่น ครีมทาผิว แชมพู หรือผลิตภัณฑ์ชะลอวัย
เปลือกอโวคาโดมี สารต้านจุลชีพและสารต้านออกซิเดชัน บางชนิดเช่นกัน แต่มีไขมันน้อยมากแทบจะไม่มีเลย บางงานวิจัยพยายามสกัดพวก polyphenols หรือสารสีธรรมชาติจากเปลือก เพื่อใช้ในอาหารเสริม หรือผลิตภัณฑ์สุขภาพ ไม่ได้สกัดน้ำมันโดยตรง แบบเนื้อผล แต่ใช้เปลือกเป็นวัตถุดิบเสริมมากกว่า เช่น ผสมในน้ำมันหลักเพื่อเพิ่มคุณสมบัติด้านสุขภาพ
ส่วนตัวคิดว่าไม่ต้องทำเองหรอกครับ ซื้อกินเหอะ 555 เจ้านี้ดีนะ อยู่คู่วงการสุขภาพมาแต่แรกๆเลย https://s.shopee.co.th/8zsnEsLrvh
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 04c915da:3dfbecc9
2025-05-16 17:12:05
@ 04c915da:3dfbecc9
2025-05-16 17:12:05One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 09fbf8f3:fa3d60f0
2024-08-13 16:06:35
@ 09fbf8f3:fa3d60f0
2024-08-13 16:06:35由于gmail在中国被防火墙拦截了,无法打开,不想错过邮件通知。
通过自建ntfy接受gmail邮件通知。 怎么自建ntfy,后面再写。
2024年08月13日更新:
修改不通过添加邮件标签来标记已经发送的通知,通过Google Sheets来记录已经发送的通知。
为了不让Google Sheets文档的内容很多,导致文件变大,用脚本自动清理一个星期以前的数据。
准备工具
- Ntfy服务
- Google Script
- Google Sheets
操作步骤
- 在Ntfy后台账号,设置访问令牌。
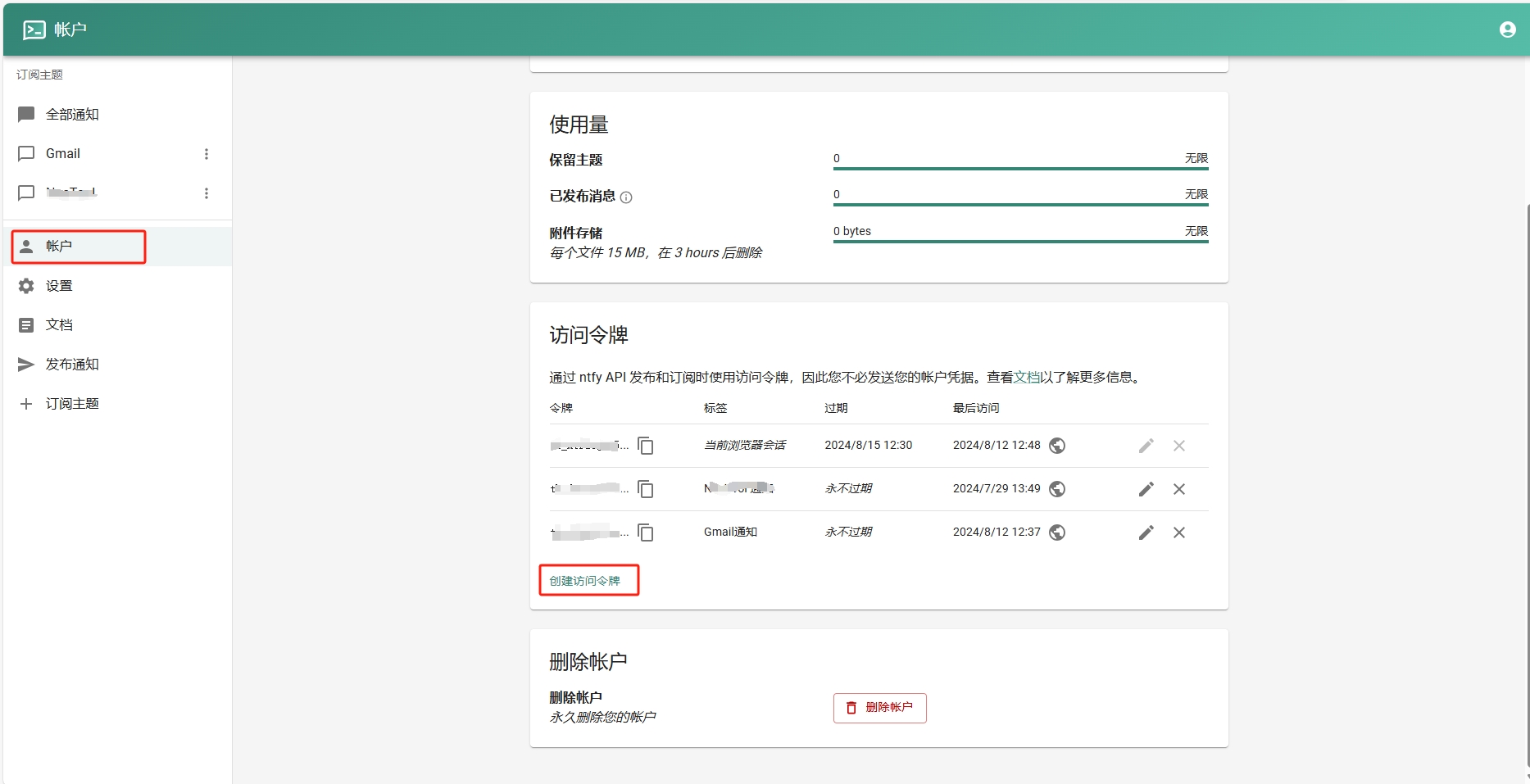
- 添加订阅主题。
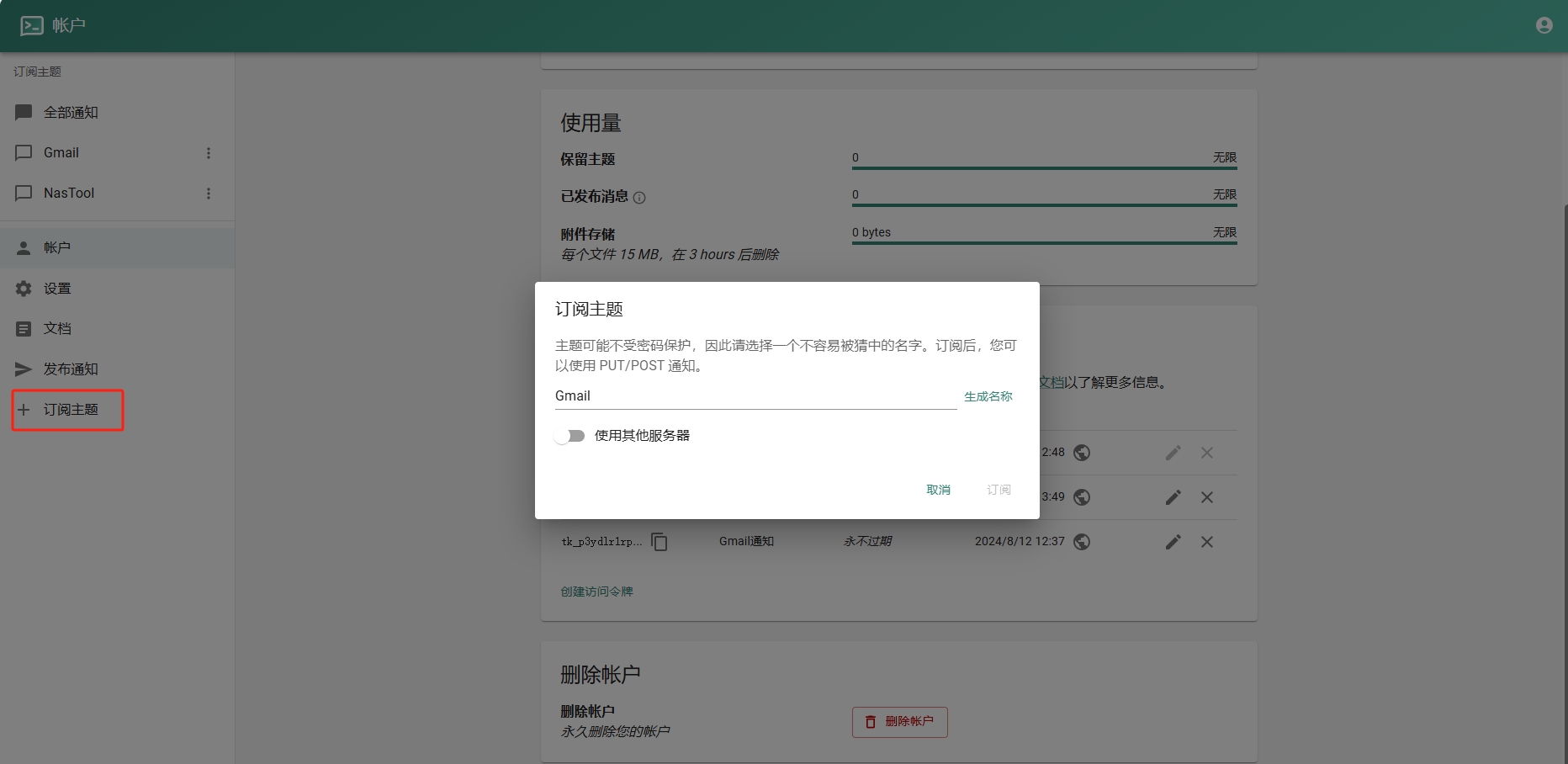
- 进入Google Sheets创建一个表格.记住id,如下图:
- 进入Google Script创建项目。填入以下代码(注意填入之前的ntfy地址和令牌):
```javascript function checkEmail() { var sheetId = "你的Google Sheets id"; // 替换为你的 Google Sheets ID var sheet = SpreadsheetApp.openById(sheetId).getActiveSheet();
// 清理一星期以前的数据 cleanOldData(sheet, 7 * 24 * 60); // 保留7天(即一周)内的数据
var sentEmails = getSentEmails(sheet);
var threads = GmailApp.search('is:unread'); Logger.log("Found threads: " + threads.length);
if (threads.length === 0) return;
threads.forEach(function(thread) { var threadId = thread.getId();
if (!sentEmails.includes(threadId)) { thread.getMessages().forEach(sendNtfyNotification); recordSentEmail(sheet, threadId); }}); }
function sendNtfyNotification(email) { if (!email) { Logger.log("Email object is undefined or null."); return; }
var message = `发件人: ${email.getFrom() || "未知发件人"} 主题: ${email.getSubject() || "无主题"}
内容: ${email.getPlainBody() || "无内容"}`;
var url = "https://你的ntfy地址/Gmail"; var options = { method: "post", payload: message, headers: { Authorization: "Bearer Ntfy的令牌" }, muteHttpExceptions: true };
try { var response = UrlFetchApp.fetch(url, options); Logger.log("Response: " + response.getContentText()); } catch (e) { Logger.log("Error: " + e.message); } }
function getSentEmails(sheet) { var data = sheet.getDataRange().getValues(); return data.map(row => row[0]); // Assuming email IDs are stored in the first column }
function recordSentEmail(sheet, threadId) { sheet.appendRow([threadId, new Date()]); }
function cleanOldData(sheet, minutes) { var now = new Date(); var thresholdDate = new Date(now.getTime() - minutes * 60 * 1000); // 获取X分钟前的时间
var data = sheet.getDataRange().getValues(); var rowsToDelete = [];
data.forEach(function(row, index) { var date = new Date(row[1]); // 假设日期保存在第二列 if (date < thresholdDate) { rowsToDelete.push(index + 1); // 存储要删除的行号 } });
// 逆序删除(从最后一行开始删除,以避免行号改变) rowsToDelete.reverse().forEach(function(row) { sheet.deleteRow(row); }); }
```
5.Google Script是有限制的不能频繁调用,可以设置五分钟调用一次。如图:
结尾
本人不会代码,以上代码都是通过chatgpt生成的。经过多次修改,刚开始会一直发送通知,后面修改后将已发送的通知放到一个“通知”的标签里。后续不会再次发送通知。
如需要发送通知后自动标记已读,可以把代码复制到chatgpt给你写。
-
 @ 8f69ac99:4f92f5fd
2025-04-01 15:54:53
@ 8f69ac99:4f92f5fd
2025-04-01 15:54:53Bitcoin tem-se afirmado como um meio de pagamento global, atraindo cada vez mais comerciantes e consumidores. Em Portugal, os pequenos e médios empresários têm uma oportunidade única para reduzir custos, expandir mercados e proteger-se da inflação ao aceitar bitcoin como opção pagamento.
Apesar das vantagens, muitos comerciantes enfrentam desafios significativos, especialmente no que toca às obrigações fiscais e à falta de conhecimento (ou vontade de aprender) por parte dos contabilistas. Questões como o registo contábil adequado, a tributação do IRC e a facturação com IVA ainda geram incerteza e dificultam a adopção da criptomoeda.
Este artigo explora como os comerciantes podem aceitar bitcoin de forma legal e eficiente, analisa os desafios fiscais e contábeis e apresenta soluções práticas para superar os obstáculos impostos pela regulamentação e pela falta de apoio dos profissionais de contabilidade.
Benefícios de Aceitar Bitcoin
1. Redução de Custos
Aceitar pagamentos em bitcoin permite evitar taxas bancárias elevadas, especialmente em transacções internacionais. Como as transferências ocorrem directamente entre carteiras digitais, sem a intermediação de bancos, os comerciantes podem poupar significativamente em comissões e taxas de processamento.
2. Liquidação Rápida
Diferente dos pagamentos bancários tradicionais, que podem demorar dias, uma transacção na rede Bitcoin pode ser confirmada em minutos, ou em segundos ou menos usando a Lightning Network. Isto reduz o tempo de espera para a disponibilidade dos fundos e melhora o fluxo de caixa dos comerciantes.
3. Expansão de Mercado
Os comerciantes podem atrair clientes internacionais e um público mais inovador e tecnológico. A aceitação de bitcoin pode diferenciar um negócio da concorrência e aumentar a base de clientes ao incluir entusiastas de criptomoedas e consumidores que preferem meios de pagamento descentralizados.
4. Protecção Contra Inflação
Bitcoin pode actuar como reserva de valor, protegendo o património contra desvalorizações monetárias. Em contextos de inflação elevada, manter parte do capital em Bitcoin pode ajudar a preservar o poder de compra a longo prazo.
|
 |
|:--:|
| Bruno de Gouveia da Care to Beauty - A Seita Bitcoin |
|
|:--:|
| Bruno de Gouveia da Care to Beauty - A Seita Bitcoin |Como Funciona na Prática?
1. Aceitação Directa vs. Conversão Automática
Os comerciantes podem optar por aceitar bitcoin directamente, mantendo-o na sua carteira digital, ou utilizar serviços como OpenNode, Swiss Bitcoin Pay, Coincorner ou Coinbase para converter automaticamente os pagamentos em euros. A escolha depende da estratégia da empresa quanto à exposição à volatilidade da criptomoeda.
2. Configuração de Carteira Bitcoin
Para receber pagamentos directamente, o comerciante precisa de uma carteira Bitcoin segura, como Electrum, BlueWallet ou Aqua entre outras. Estas carteiras oferecem diferentes níveis de segurança e acessibilidade, permitindo que os comerciantes escolham a solução mais adequada ao seu modelo de negócio.
3. Facturação e Registo Contábil
Cada pagamento deve ser facturado em euros, com referência à taxa de câmbio do momento. O registo contábil deve ser feito correctamente para garantir a conformidade fiscal, reflectindo o valor recebido em bitcoin e a sua equivalência em euros na altura da transacção. Muitas carteiras e plataformas de pagamento oferecem relatórios detalhados que facilitam o registo contábil e a declaração fiscal.
Obrigações Fiscais e Contábeis
1. IRC (Imposto sobre o Rendimento das Pessoas Colectivas)
Os rendimentos obtidos através de bitcoin devem ser devidamente registados na contabilidade da empresa, uma vez que são considerados receitas operacionais. Para efeitos fiscais, a conversão do valor recebido em bitcoin deve ser feita com base na taxa de câmbio vigente no momento da transacção, garantindo um registo transparente e conforme com as normas contábeis.
Se a empresa optar por manter os bitcoins sem os converter imediatamente para euros, estes podem ser classificados como activos intangíveis, conforme a Norma Contabilística e de Relato Financeiro (NCRF), artigo 6. No entanto, se forem utilizados como meio de pagamento recorrente, por exemplo pagar a fornecedores que também aceitem bitcoin, podem ser classificados como inventário, dependendo da natureza da actividade empresarial.
No momento da venda ou conversão dos bitcoins para euros, qualquer mais-valia obtida é considerada um rendimento da empresa e estará sujeita a tributação em sede de IRC à taxa geral em vigor.
2. IVA (Imposto sobre o Valor Acrescentado)
As transacções de troca de bitcoin por euros estão isentas de IVA, conforme o artigo 9.º, alínea 27), subalínea d), do Código do IVA (CIVA), que reconhece as criptomoedas como meios de pagamento e as exclui da incidência de IVA.
No entanto, a venda de bens ou serviços pagos em bitcoin deve ser facturada normalmente, em euros, com a taxa de IVA correspondente ao produto ou serviço comercializado. Para garantir conformidade fiscal, a factura deve indicar a contrapartida em euros, com base na taxa de câmbio do momento da transacção, independentemente da moeda utilizada no pagamento.
Na prática, aceitar pagamento em bitcoin funciona de forma muito semelhante a aceitar pagamento em dinheiro físico... 😉
3. Registos e Demonstrações Financeiras
As empresas que aceitam bitcoin devem manter registos contabilísticos detalhados sobre todas as transacções realizadas. bitcoin pode ser registado como activo intangível ou inventário, dependendo do seu uso:
- Activo intangível: Quando a empresa detém bitcoin como reserva de valor ou investimento, registando-o ao custo de aquisição e procedendo a ajustamentos caso haja desvalorização relevante.
- Inventário: Se a empresa opera no sector de compra e venda de criptomoedas ou usa bitcoin para transacções comerciais frequentes, deve ser registado como inventário, seguindo as regras de mensuração aplicáveis a mercadorias.
As demonstrações financeiras devem reflectir correctamente a posse de bitcoin, incluindo informações sobre variações de valor ao longo do tempo. Os contabilistas devem garantir a correta apresentação destes activos nos balanços e relatórios anuais, o que pode exigir reavaliação periódica dos valores contabilizados.
O Obstáculo: Contabilistas e a Falta de Apoio
1. Falta de Conhecimento
Muitos TOC não estão familiarizados com a contabilidade de criptomoedas, o que gera incertezas e complicações para os comerciantes.
2. Resistência e Falta de Vontade
Em vez de se actualizarem, muitos contabilistas recusam-se a aprender sobre Bitcoin, deixando os comerciantes sem apoio adequado.
3. Impacto nos Negócios
Com a falta de informação e apoio dos TOC, muitos comerciantes evitam aceitar bitcoin, perdendo uma oportunidade de mercado.
Soluções e Alternativas
1. Educação e Autonomia
Os comerciantes podem aprender o essencial sobre contabilidade de bitcoin para questionar e orientar os seus contabilistas. Existem recursos online, cursos e materiais educativos que permitem aos empresários compreender as melhores práticas para registo e declaração das transacções em bitcoin.
2. Ferramentas e Software
Existem algumas plataformas que ajudam na gestão e declaração de criptomoedas, fornecendo relatórios detalhados sobre transacções, ganhos e impostos devidos. Essas ferramentas facilitam a organização financeira e reduzem erros contábeis.
3. Rede de Apoio
Juntar-se a comunidades de empresários e especialistas em bitcoin pode ajudar a encontrar soluções e recomendações de contabilistas competentes. Fóruns, grupos em redes sociais e associações focadas no tema podem ser excelentes fontes de suporte e partilha de experiências.
4. Links uteis
Conclusão
Aceitar bitcoin pode ser vantajoso para pequenos e médios comerciantes, mas a burocracia e a falta de conhecimento dos contabilistas dificultam esse processo. É essencial que os comerciantes exijam um melhor serviço dos seus TOC e procurem alternativas para garantir que estão em conformidade com a lei, aproveitando ao mesmo tempo os benefícios desta nova forma de pagamento.
Disclaimer: Este artigo é meramente informativo e não deve ser considerado como aconselhamento jurídico ou fiscal. É recomendável consultar um profissional qualificado para obter orientações específicas sobre a aceitação de bitcoin e as obrigações fiscais associadas. A legislação pode variar e é importante estar sempre actualizado com as normas vigentes. A responsabilidade pela aceitação de bitcoin e o cumprimento das obrigações fiscais recai exclusivamente sobre o comerciante. O autor não se responsabiliza por quaisquer consequências decorrentes da aceitação de bitcoin ou da interpretação das informações contidas neste artigo.
Photo by CardMapr.nl on Unsplash
-
 @ 502ab02a:a2860397
2025-05-21 02:12:10
@ 502ab02a:a2860397
2025-05-21 02:12:10ถ้าเอ่ยถึง CJ หลายคนอาจนึกถึงซอสเกาหลีรสจัดจ้าน หรือบะหมี่กึ่งสำเร็จรูปแบรนด์ดังที่ขายทั่วโลก แต่เบื้องหลังความสำเร็จของแบรนด์เหล่านั้น มีบริษัทแม่อย่าง CJ CheilJedang ที่ไม่ได้แค่ผลิตอาหารแปรรูป แต่เป็นหนึ่งในผู้เล่นใหญ่ของอุตสาหกรรมอาหารระดับโลก ด้วยฐานความรู้ลึกซึ้งในเทคโนโลยีชีวภาพ หนึ่งในแขนงที่โดดเด่นคือ CJ BIO ธุรกิจไบโอเทคโนโลยีที่เน้นการใช้ Microbial Fermentation หรือการหมักจุลินทรีย์เพื่อผลิตสารอาหารและวัตถุดิบอาหารคุณภาพสูงในระดับอุตสาหกรรม
ประวัติของ CJ BIO เริ่มจากจุดเล็ก ๆ แต่ทรงพลัง คือการผลิต โมโนโซเดียมกลูตาเมต (MSG) ซึ่งเป็นกรดอะมิโนชนิดหนึ่งที่มีบทบาทสำคัญในการเพิ่มรสชาติ “อูมามิ” ให้กับอาหารทั่วโลก จุดนี้เองที่ทำให้ CJ BIO ได้สะสมเทคโนโลยีหมักจุลินทรีย์ในระดับอุตสาหกรรมมายาวนานกว่า 60 ปี ด้วยโรงงานหมักขนาดใหญ่ที่ตั้งอยู่ในหลายประเทศ เช่น เกาหลีใต้ จีน บราซิล อินโดนีเซีย และสหรัฐอเมริกา ทำให้ CJ BIO กลายเป็นหนึ่งในผู้ผลิตกรดอะมิโนและวัตถุดิบอาหารหมักจุลินทรีย์รายใหญ่ของโลก
แต่ถ้าให้พูดแบบง่าย ๆ การหมักจุลินทรีย์ของ CJ BIO นั้น ไม่ใช่แค่ “การทำอาหาร” ธรรมดา ๆ แต่เป็นการ “สร้างอาหารในระดับโมเลกุล” ตั้งแต่พื้นฐาน ซึ่งถือเป็นเทคโนโลยีที่สำคัญสำหรับอนาคตของอาหาร เพราะมันช่วยให้เราสามารถผลิตโปรตีน กรดอะมิโน และสารอาหารต่าง ๆ ที่มีคุณภาพสูงและควบคุมได้ในโรงงานขนาดใหญ่ โดยไม่ต้องพึ่งพาการเกษตรแบบดั้งเดิมที่ต้องใช้พื้นที่มากและมีผลกระทบต่อสิ่งแวดล้อม
เมื่อเทรนด์โลกกำลังเปลี่ยนไปในทางที่ผู้บริโภคหันมาใส่ใจสุขภาพและสิ่งแวดล้อมมากขึ้น เรื่อง “อาหารจากห้องแล็บ” หรือ “อาหารเทคโนโลยีชีวภาพ” จึงกลายเป็นสิ่งที่ได้รับความสนใจอย่างมาก และนี่เองที่ทำให้ CJ BIO ไม่ได้หยุดอยู่แค่ Microbial Fermentation แบบดั้งเดิม แต่เริ่มขยับเข้าสู่โลกใหม่ของ Precision Fermentation การใช้จุลินทรีย์ที่ผ่านการดัดแปลงพันธุกรรมอย่างแม่นยำ เพื่อผลิตโปรตีนหรือสารอาหารเฉพาะอย่างที่ต้องการ
ความเคลื่อนไหวที่สำคัญเกิดขึ้นในปี 2022 เมื่อ CJ CheilJedang ประกาศลงทุนใน New Culture สตาร์ทอัพสัญชาติอเมริกันที่กำลังพัฒนา “ชีสไร้วัว” ด้วยเทคโนโลยี Precision Fermentation ซึ่ง New Culture ใช้จุลินทรีย์ที่ถูกออกแบบมาเพื่อผลิตโปรตีนเคซีน โปรตีนหลักในน้ำนมวัว โดยไม่ต้องมีวัวจริงเลย นั่นหมายความว่าชีสที่ผลิตออกมาจะไม่มีส่วนผสมจากสัตว์จริง ๆ แต่ยังคงรสชาติและเนื้อสัมผัสเหมือนชีสธรรมชาติทุกประการ
การลงทุนครั้งนี้ของ CJ CheilJedang บริษัทแม่ของ CJ BIO จึงถือเป็นการผนึกกำลังระหว่างเทคโนโลยีดั้งเดิมที่ผ่านการพิสูจน์แล้วในระดับอุตสาหกรรม กับนวัตกรรมที่พร้อมเปลี่ยนแปลงวงการอาหารครั้งใหญ่
ถ้าให้เปรียบเทียบง่าย ๆ CJ BIO เหมือนกับ “โรงงานปั้นโมเลกุลอาหาร” ที่มีความเชี่ยวชาญสูงในการจัดการกับจุลินทรีย์และการผลิตกรดอะมิโนหลากหลายชนิด โดยเฉพาะ MSG ซึ่งถือเป็น “พี่ใหญ่” ในกลุ่มกรดอะมิโนที่ช่วยเพิ่มรสชาติและถูกใช้ในอุตสาหกรรมอาหารทั่วโลก
ความเชี่ยวชาญในการผลิต MSG นี้เอง คือฐานกำลังสำคัญที่ทำให้ CJ BIO สามารถขยายขอบเขตไปสู่การผลิตโปรตีนด้วย Precision Fermentation ได้อย่างมั่นใจ เพราะกระบวนการหมักจุลินทรีย์เพื่อผลิตกรดอะมิโนและโปรตีนนั้นมีความคล้ายคลึงกันในเชิงเทคนิคและการควบคุมคุณภาพ
CJ BIO มีโรงงานหมักจุลินทรีย์ที่ทันสมัยและขนาดใหญ่กระจายอยู่ทั่วโลก สามารถผลิตวัตถุดิบในปริมาณมหาศาลเพื่อตอบสนองตลาดอาหารที่เติบโตอย่างรวดเร็ว และการมีเครือข่ายโรงงานแบบนี้ทำให้ CJ BIO มีความได้เปรียบในการลดต้นทุนและควบคุมคุณภาพอย่างเข้มงวด
อนาคตที่ CJ BIO กำลังเดินไปนั้น ไม่ใช่แค่การผลิตวัตถุดิบอาหารธรรมดา ๆ แต่คือการสร้างนวัตกรรมที่จะเปลี่ยนแปลงวิธีการผลิตและการบริโภคอาหารของโลก
เมื่อผลิตภัณฑ์จากเทคโนโลยี Precision Fermentation อย่างชีสไร้วัว ไข่ไร่ไก่ หรือโปรตีนทางเลือกต่าง ๆ เริ่มเข้ามาในตลาดมากขึ้น เราอาจจะได้เห็น CJ BIO ทำหน้าที่เหมือน “Intel Inside” ของวงการอาหารอนาคต ที่อยู่เบื้องหลังผลิตภัณฑ์สำคัญ ๆ ที่ผู้บริโภคชื่นชอบโดยไม่รู้ตัว
นี่คือเหตุผลที่ทำให้การมองแค่แบรนด์อาหารหรือการตลาดที่พูดถึง “ความยั่งยืน” หรือ “อาหารปลอดสัตว์” ยังไม่พอ เราต้องมองให้ลึกไปถึงระบบนิเวศของเทคโนโลยีและทุนที่อยู่เบื้องหลัง เพราะนั่นคือเกมกระดานใหญ่ที่กำลังขยับเปลี่ยนแปลงวงการอาหารโลกอย่างแท้จริง
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 35f3a26c:92ddf231
2024-08-13 15:52:59
@ 35f3a26c:92ddf231
2024-08-13 15:52:59Share!
https://video.nostr.build/9217eb6231f0c18055329679f582b41b60e4e74359ba0d86b040f45ffaa480ae.mp4
originally posted at https://stacker.news/items/647261
-
 @ 04c915da:3dfbecc9
2025-03-04 17:00:18
@ 04c915da:3dfbecc9
2025-03-04 17:00:18This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ 0971cd37:53c969f4
2025-05-20 17:00:53
@ 0971cd37:53c969f4
2025-05-20 17:00:53ลดต้นทุนค่าไฟ เพิ่มความคุ้มค่าให้การขุด Bitcoin ที่บ้าน ในยุคที่ต้นทุนพลังงานสูงขึ้นอย่างต่อเนื่อง นักขุด Bitcoin ที่บ้าน หรือ Home Miner ต้องคิดให้รอบคอบก่อนเลือกเครื่องขุด เพราะ “แรงขุดสูงสุด” ไม่ได้แปลว่า “กำไรดีที่สุด” อีกต่อไป การเลือกเครื่องขุดไม่ใช่แค่ดูแค่แรงขุด (Hashrate) สูงสุดเท่านั้น แต่ต้องพิจารณาเรื่อง "การกินไฟ" และ "ความคุ้มค่าในการใช้งานระยะยาว" ด้วย ซึ่งสายหนึ่งที่ได้รับความนิยมมากขึ้นเรื่อย ๆ ก็คือ สาย Tuning Power หรือการจูนเครื่องขุดเพื่อให้ได้อัตราส่วน Hashrate/Watt ที่ดีที่สุด
เทรนด์ใหม่ของวงการขุดคือสาย Tuning Power หรือการปรับแต่งพลังงานของเครื่องขุด Bitcoin (ASIC) ให้ได้ ประสิทธิภาพ Hashrate ต่อการใช้พลังงาน (Efficiency) สูงที่สุด ซึ่งเหมาะอย่างยิ่งสำหรับการขุดในบ้านที่มีข้อจำกัดด้านค่าไฟ ความร้อน และ เสียงรบกวน
Tuning Power คืออะไร? Tuning Power คือการปรับลดแรงขุดของเครื่อง ASIC ลงเล็กน้อย เพื่อให้กินไฟน้อยลงแบบชัดเจน
ตัวอย่างเช่น Custom Firmware Braiins OS ใช้กับ Antminer S19jpro จากเดิมแรงขุด 104 TH/s กินไฟ 3,500W เมื่อปรับแต่งในส่วน Power Target จูนเหลือ 75 TH/s อาจกินไฟแค่ 1,600W-1,800W หลังจาก Tuning ค่าประสิทธิภาพ(Efficiency)ดีขึ้น เช่น จาก 32 J/TH เหลือเพียง 22–20 J/TH
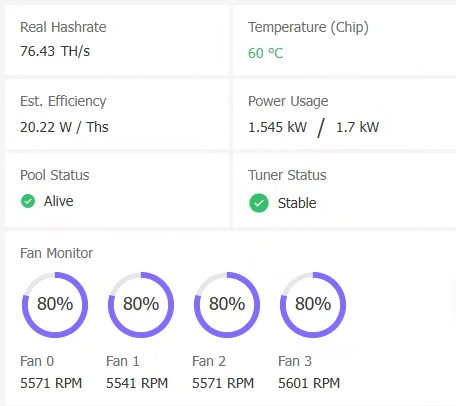 หมายเหตุ: ค่า Efficiency ยิ่งต่ำ ยิ่งดี แปลว่าใช้พลังงานน้อยต่อ 1 TH
หมายเหตุ: ค่า Efficiency ยิ่งต่ำ ยิ่งดี แปลว่าใช้พลังงานน้อยต่อ 1 THทำไมต้อง Tuning Power? การจูนพลังงาน (Tuning Power) คือการปรับแต่งเครื่องขุด เช่น ASIC ให้ทำงานที่แรงขุดไม่เต็ม 100% แต่กินไฟน้อยลงอย่างชัดเจน ส่งผลให้:
- ประหยัดค่าไฟ โดยเฉพาะถ้าขุดในพื้นที่ต้นทุนพลังงานค่าไฟสูงหรือไม่มี TOU (Time of Use) และ เหมาะสำหรับผู้ใช้ไฟแบบ TOU ที่ค่าไฟกลางวัน ON-Peak แพง ต้องการขุดเลือกช่วงกลางคืนและวันหยุดเสาร์-อาทิตย์ และ วันหยุดราชการตามปกติ Off-Peak , ที่ใช้ระบบ Solar หรือมีระบบ Battery ต้องการประหยัดไฟ
- ลดความร้อนของเครื่อง ทำให้ยืดอายุการใช้งานและลดค่าใช้จ่ายด้าน ซำบำรุง ระบบระบายความร้อน
- เพิ่มความคุ้มค่า ในช่วงตลาดหมี ที่กำไรจากการขุดต่ำ การลดต้นทุนไฟฟ้าคือทางรอดหลัก
เครื่องขุด Bitcoin (ASIC) รุ่นไหน ที่เหมาะกับสาย Tuning Power
-
Antminer รองรับ Custom Firmware เช่น Braiins OS ที่เป็นยอดนิยมในการ Tuning Power
-
WhatsMiner M30-M60s Series ขึ้นไป ใช้โปรแกรม WhatsMinerTool เพื่อทำการ Tuning Power ได้โดยตรงไม่จำเป็นต้อง Custom Firmware
สรุป การเป็น Home Miner ที่ยั่งยืนไม่ได้ขึ้นกับว่าเครื่องขุดแรงแค่ไหน แต่ขึ้นกับว่า “จ่ายค่าไฟแล้วเหลือกำไรหรือไม่ หรือ จ่ายค่าไฟแล้วคุ้มค้ารายได้ Bitcoin จากการขุดจำนวนที่ได้รับมากขึ้นหรือไม่” การเลือกเครื่องขุดสำหรับสาย Tuning Power จึงเป็นทางเลือกที่ตอบโจทย์ผู้ที่ต้องการประสิทธิภาพสูงในต้นทุนที่ควบคุมได้โดยเฉพาะในยุคที่ตลาดผันผวน และ ค่าไฟฟ้าคือศัตรูตัวจริงของนักขุด
-
 @ a9434ee1:d5c885be
2024-08-13 15:50:57
@ a9434ee1:d5c885be
2024-08-13 15:50:57Markdown + X, Y, Z is a problem, but Markdown + N can fix that.
Where N = any type of Nostr event.Whatever Markup language you choose, people will be referencing other Nostr events in it all the time. Since apps have to find ways to display those events (or the links to them) anyway, we mights as well use that as an opportunity.
Why can't Tables, for example, be embedded Nostr events?
Switching from Markdown to Asciidocs (because it has tables and some more technical stuff) still doesn’t make Tables a great experience. On mobile, Tables are notoriously hard to display in a useful way. It depends on the use case, size of the table, etc….
Creators need guarantees on these things being displayed the way they intended.
There’s a reason why most authors just embed pictures of tables instead. It has little to do with Markdown not really supporting tables and more with them ensuring readability and appropriate styling.So what if you enhance Markdown not only with embedded Nostr Events but also with something like Hypernotes Widgets that serve as a preview/display for those Nostr Events?
That way: - you are still using the most simple and popular markup language - devs “only” have to implement one extra thing (Hypernotes) that handles all the complexity and extensibility from there - authors can create articles and wiki entries with interactive elements in them, can have the guarantee that they display properly, can use any styling that suits them, etc… - the worst case scenario of reading it in a random crappy app still displays the link to the event (including it's explanatory metadata)
Imagine custom interactive graphs, polls, media players, products, … embedded in articles BUT limited to the Nostr-verse for all interaction and data fetching.
(this article will be updated with UI prototypes and further thoughts)
-
 @ 8f69ac99:4f92f5fd
2025-03-14 11:13:38
@ 8f69ac99:4f92f5fd
2025-03-14 11:13:38O Banco Central Europeu (BCE) está a intensificar a sua propagan... a sua campanha a favor do euro digital, apresentando-o como uma evolução necessária do dinheiro. Mas trata-se realmente de conveniência ou há uma agenda oculta? Vamos desmontar os argumentos do BCE e perceber por que razão esta moeda digital de banco central (CBDC) tem mais a ver com controlo do que com inovação financeira.
Argumento 1: 'A nossa moeda precisa de acompanhar a forma como queremos pagar.'
O BCE afirma que mais de metade dos europeus prefere pagamentos digitais, mas ignora o facto de que esses pagamentos já existem. Desde cartões bancários a PayPal, transferências SEPA, Apple Pay e Google Pay, não faltam opções. Em 2020 já 60% de todos os pagamentos na UE foram digitais, segundo dados do BCE.
O que não mencionam é que o euro digital será controlado pelo Estado (ou neste caso o BCE e a UE que são efectivamente um governo supranacional, não eleito) e programável. Ao contrário do dinheiro físico, que permite verdadeira autonomia financeira, uma CBDC permitirá ao governo monitorizar, condicionar e até restringir os teus gastos.
Já Bitcoin oferece há mais de 16 anos uma solução global, descentralizada e sem necessidade de permissão, sem precisar de supervisão estatal.
Argumento 2: 'Os europeus poderão usar o euro digital ao lado do dinheiro físico.'
A história mostra-nos que, sempre que surgem alternativas digitais estatais, o dinheiro físico acaba por ser eliminado. Restrições a levantamentos, proibições de transacções em numerário e a desvalorização do dinheiro físico são tácticas comuns para empurrar as pessoas para pagamentos digitais controlados.
Bitcoin não precisa de autorização e pode ser usado de forma independente do sistema bancário. Continua a ser a única forma de dinheiro digital realmente descentralizada, garantindo soberania financeira aos indivíduos.
Argumento 3: 'O euro digital garantirá privacidade e confiança.'
O BCE já admitiu que o anonimato total não é uma opção no euro digital. Ao contrário do dinheiro físico, que permite transacções privadas, uma CBDC será totalmente rastreável. Cada transacção será monitorizada, armazenada e potencialmente sujeita a restrições ou impostos.
Já Bitcoin oferece pseudonimato e resistência à censura. Nenhuma entidade central pode bloqueá-lo, congelá-lo ou controlá-lo, tornando-o a melhor opção para pagamentos digitais livres.
Argumento 4: 'O euro digital funcionará offline, sem internet ou electricidade.'
Embora o BCE afirme que o euro digital terá funcionalidade offline, qualquer transacção terá de ser reconciliada online mais tarde, o que significa que a privacidade continua a ser uma ilusão. Além disso, essa funcionalidade offline será provavelmente limitada a pequenos valores pré-carregados—nada de revolucionário.
Já Bitcoin pode ser enviado via ondas de rádio, redes mesh e até satélites, ou opções como o LNURL ou mesmo ecash, tornando-o mais resiliente do que qualquer moeda digital, governamental ou não.
Argumento 5: 'Precisamos de uma legislação forte para apoiar o euro digital.'
Se o euro digital fosse realmente útil, por que razão precisa de ser imposto por lei? Bitcoin cresceu de forma orgânica porque funciona. O BCE está a pressionar por leis que poderão, no futuro, tornar as CBDCs a única forma legal de dinheiro digital, eliminando a liberdade financeira.
Bitcoin, por sua vez, é imparável, descentralizado e independente de decisões políticas. Nenhuma autoridade central pode decidir como deve, e se pode, usá-lo.
Conclusão: O Euro Digital Não É O Que Parece
O euro digital não se trata de inovação, mas de controlo. Os europeus já têm métodos de pagamento digitais eficientes, e o dinheiro físico garante a verdadeira privacidade financeira. Uma moeda digital estatal introduz o risco de vigilância financeira, restrições de gastos e dinheiro programável, onde o governo pode decidir quando, onde e como podes gastar o teu dinheiro.
Entretanto, Bitcoin já funciona há mais de 16 anos como uma alternativa descentralizada e global, sem precisar da aprovação de bancos centrais. Garante soberania financeira e resistência à censura, tornando-se a verdadeira forma de dinheiro digital do futuro.
A questão não é se o euro digital tornará os pagamentos mais fáceis—mas se tornará a liberdade financeira impossível.
-
 @ 1c9dcd8f:1852f704
2024-08-13 13:53:16
@ 1c9dcd8f:1852f704
2024-08-13 13:53:16Many strange spells are effected by the means of a dead man’s hand—chiefly to produce butter in the churn. The milk is stirred round nine times with the dead hand, the operator crying aloud all the time, “Gather! gather! gather!” While a secret form of words is used which none but the initiated know.
Another use is to facilitate robberies. If a candle is placed in a dead hand, neither wind nor water can extinguish it. And if carried into a house the inmates will sleep the sleep of the dead as long as it remains under the roof, and no power on earth can wake them while the dead hand holds the candle.
For a mystic charm, one of the strongest known is the hand of an unbaptized infant fresh taken from the grave in the name of the Evil One.
A dead hand is esteemed also a certain cure for most diseases, and many a time sick people have been brought to a house where a corpse lay that the hand of the dead might be laid on them.
--
The souls of the dead who may happen to die abroad, greatly desire to rest in Ireland. And the relations deem it their duty to bring back the body to be laid in Irish earth. But even then the dead will not rest peaceably unless laid with their forefathers and their own people, and not amongst strangers.
A young girl happened to die of a fever while away on a visit to some friends, and her father thought it safer not to bring her home, but to have her buried in the nearest churchyard. However, a few nights after his return home, he was awakened by a mournful wail at the window, and a voice cried, “I am alone; I am alone; I am alone!” Then the poor father knew well what it meant, and he prayed in the name of God that the spirit of his dead child might rest in peace until the morning. And when the day broke he arose and set off to the strange burial ground, and there he drew the coffin from the earth, and had it carried all the way back from Cork to Mayo; and after he had laid the dead in the old graveyard beside his people and his kindred, the spirit of his child had rest, and the mournful cry was no more heard in the night.
The corner of a sheet that has wrapped a corpse is a cure for headache if tied round the head.
The ends of candles used at wakes are of great efficacy in curing burns.
A piece of linen wrap taken from a corpse will cure the swelling of a limb if tied round the part affected.
It is believed that the spirit of the dead last buried has to watch in the churchyard until another corpse is laid there; or has to perform menial offices in the spirit world, such as carrying wood and water until the next spirit comes from earth. They are also sent on messages to earth, chiefly to announce the coming death of some relative, and at this they are glad, for then their time of peace and rest will come at last.
If any one stumbles at a grave it is a bad omen; but if he falls and touches the clay, he will assuredly die before the year is out.
Any one meeting a funeral must turn back and walk at least four steps with the mourners.
If the nearest relative touches the hand of a corpse it will utter a wild cry if not quite dead.
On Twelfth Night the dead walk, and on every tile of the house a soul is sitting, waiting for your prayers to take it out of purgatory.
There are many strange superstitions in the western islands of Connemara. At night the dead can be heard laughing with the fairies and spinning the flax. One girl declared that she distinctly heard her dead mother’s voice singing a mournful Irish air away down in the heart of the hill. But after a year and a day the voices cease, and the dead are gone for ever.
It is a custom in the West, when a corpse is carried to the grave, for the bearers to stop half way, while the nearest relatives build up a small monument of loose stones, and no hand would ever dare to touch or disturb this monument while the world lasts.
When the grave is dug, a cross is made of two spades, and the coffin is carried round it three times before being placed in the clay. Then the prayers for the dead are said, all the people kneeling with uncovered head.
-
 @ 6bae33c8:607272e8
2024-08-13 10:56:57
@ 6bae33c8:607272e8
2024-08-13 10:56:57I’ve written about this before. The point of this league isn’t the meager $50 entry fee and the modest prize for winning it. It’s avoiding the downside of losing the steakhouse side bet wherein you foot the bill (one year I paid $520) for a bunch of greedy gluttonous douches who stuff their faces on your dime.*
It’s a 14-team, half-PPR auction, with IDPs instead of team defenses. Here are the results:
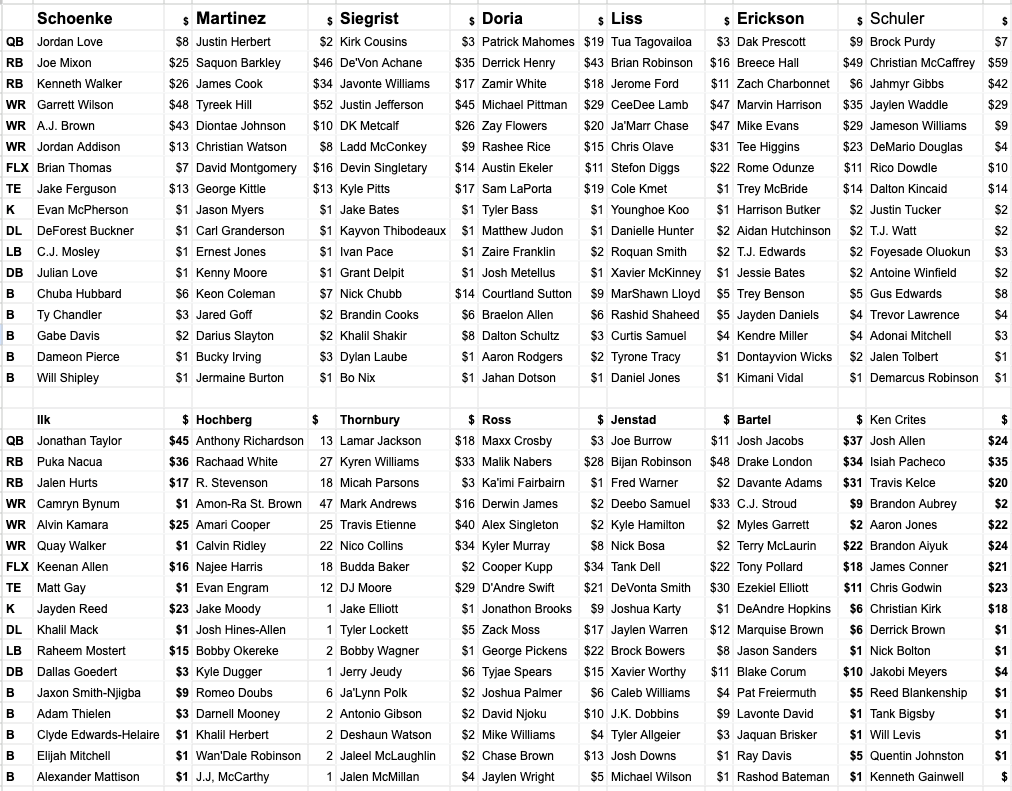
*It’s well known I’m the greediest most gluttonous douche when I win the bet, and that is often.
My strategy was to buy three elite receivers and skimp everywhere else. It was going well until I price-enforced on Chris Olave (who I hate at his second-round ADP) and got stuck for $31. I would much rather have gone the extra mile for a $47 Amon-Ra St. Brown or spent it instead on a running back.
I thought I’d be able to get RBs cheap late too, but that wasn’t the case. After bowing out on an $18 Rhamondre Stevenson, I found myself bidding up Brian Robinson (who I like) to $16. And I wanted to pair Jerome Ford ($11) with Nick Chubb ($14), but he too got out of reach late.
Everything else went fine. I spent $4 combined on Tua Tagovailoa and Danny Dimes who in this running-QB-friendly format has more value. I also got Rashid Shaheed late because I think he’s a better player in real life than Olave and felt like I needed the insurance after that mistake.
All things considered, the draft was fine — CeeDee Lamb and Ja’Marr Chase are two top-seven overall picks, Olave is a second rounder and Stefon Diggs goes late third-early fourth, and that’s in the NFFC’s 12-team format, though unlike this, it’s full PPR.
-
 @ 04c915da:3dfbecc9
2025-02-25 03:55:08
@ 04c915da:3dfbecc9
2025-02-25 03:55:08Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 6ad3e2a3:c90b7740
2024-08-13 10:30:36
@ 6ad3e2a3:c90b7740
2024-08-13 10:30:36From the ages of 8-11, I spent my summers in Saltaire, Fire Island, a tiny town across the bay from Bayshore Long Island, accessible only by ferry. I vaguely recall the first summer our parents enrolled my younger brother Damon and me in day camp where they made us swim in the cold, jelly-fish-ridden bay water early in the morning. We quit the camp within the week and were largely left to our own devices after that.
The island didn’t have cars, so you got around by bike. That meant it was safe for kids, and late-70s/early-80s parents could check out entirely. By the time I was 10 or 11, I would wake up whenever it suited me, scarf down a bowl of cereal, grab my bike and return for dinner. No one knew where we were — though the baseball field was a good bet — and no one cared.
I remember one time we brought a two-man inflatable raft to the ocean on a choppy day and had the bright idea to ride the waves in it. We got so destroyed by one wave, Damon wound up face-down in the sand underneath the raft. He was crying, but no real harm done.
. . .
To this day, I often find myself projecting into the future. “In 12 hours, I’ll be back in Lisbon, in 48 hours, I’ll be done with my running for the week, in 72 hours, etc.” And when the time comes, and I’m done with whatever travel or unpleasant task, I’ll start all over again.
If you tell this to someone, they’ll often say, “You need to be in the present.” Yeah no shit. That’s like telling someone you’re an alcoholic and them saying, “You should stop drinking.” It’s a bad habit, I’m aware. But where did this habit come from, and why is it so entrenched?
. . .
My summers were a stark contrast to the school year where like everyone else I was up at 7:00 am, exhausted and forced to sit through class after class all day, the teachers droning on about something in which I had no interest. I remember watching the clock, as though trying to make the hands move faster with my mind. Only 20 minutes left, only 10 minutes, only five. Thank God it’s Friday.
. . .
I’ve never had a real job. I worked on the Truckee River one summer blowing up rafts, stacking them on trucks and putting people in the water. I cleaned houses one summer, I worked for free during law school for the NY Attorney General’s office, I ghost wrote car blurbs for Motor Trend and Car And Driver and then I worked for RotoWire (in fantasy sports) for 22 years before we sold it. The idea of grinding away at a law firm or some other joyless menial mental labor filled me with dread. Even tedious tasks like editing our annual NFL magazine, going over the copy word by word four or five times was torture. And I had a dream job and owned part of the company.
. . .
I partied a lot in my 20s and 30s, and it was not without consequence. I have a beautiful 12-YO daughter now, but we started too late to have more than one kid. Had I known then what I know now, I would have started a big family much earlier. I would have been more serious and made it a priority. But even though I wasn’t exactly an alcoholic, I had a strong urge to use the weekend as an escape. It was my time, and I wanted to use it to chase the pleasures that were denied to me during the slog of the work week.
. . .
For parents, school is kid storage, but for kids like me it was prison. My biggest takeaway was there are dreadful, pointless things society wants from you, and you should get those done with the least possible effort so you could do whatever you wanted later. That life is divided into appeasing the machine and having fun, and the problem to solve was how to get rich despite having a very low tolerance for appeasement. The point of getting rich was to do whatever you wanted whenever you wanted and to dispense with the dreadful, pointless things forever.
. . .
Now that I have no job, and the dreadful, pointless things are kept to a minimum, I mostly do whatever I want. But the younger version of me would be surprised to know that includes running at the track three times a week, doing pull-ups at the local park, writing and editing my own essays, learning and using to the extent I’m capable the challenging new freedom tech protocols (bitcoin and nostr.) I’ve largely stopped drinking, almost never smoke weed, fast once a week, am gluten-free, rarely eat junk food, don’t drive a fancy car. I save rather than spend most of my money.
There is nothing from which to escape and nowhere to go anymore. And yet my mind still projects into the future, perpetuating the dichotomy between obligations and leisure, indentured servitude and escapism. It’s as if I’m back in Saltaire, the whole day every day in front of me, but it’s only June, and I haven’t yet adjusted fully to the reality that school’s out, and it’s really, actually summer.
Just as soon as I post this essay, walk the dog, do my pull-ups at the park, I’ll start to relax and enjoy myself.
-
 @ 8f69ac99:4f92f5fd
2025-03-12 19:02:01
@ 8f69ac99:4f92f5fd
2025-03-12 19:02:01Durante décadas, os europeus foram incentivados a poupar para o futuro — para a reforma, a compra de casa ou segurança financeira. Mas agora, a Comissão Europeia quer redefinir a poupança — não como património pessoal, mas como um recurso para investimento controlado pelo Estado.
A União de Poupanças e Investimentos (Savings and Investments Union, ou SIU), um plano que integra a União dos Mercados de Capitais e a União Bancária. Oficialmente, trata-se de “empoderar os cidadãos” e “desbloquear oportunidades de investimento”. Na realidade, trata-se de uma mudança radical rumo ao controlo financeiro, onde as suas poupanças são pressionadas ou mesmo desviadas para investimentos aprovados pelo Estado.
Ao mesmo tempo, o euro digital será lançado em Outubro de 2025. Esta moeda programável tornará os juros negativos, os controlos de capital e as restrições de gastos mais fáceis de aplicar do que nunca. A mensagem é clara: a UE está a desmantelar a autonomia financeira. O que antes eram as suas poupanças privadas pode em breve tornar-se uma ferramenta económica gerida pelo Estado.
Será apenas mais uma medida burocrática ou o primeiro passo para uma distopia financeira? Vamos analisar.
O Plano: "Transformar Poupanças Privadas em Investimento"
A declaração de Ursula von der Leyen — "Vamos transformar poupanças privadas em investimento muito necessário" — parece um plano inofensivo para impulsionar a economia. Mas, na realidade, assinala uma tomada de controlo estatal da riqueza pessoal.
Os governos desconfiam da independência financeira. Quando os indivíduos poupam por conta própria, fazem escolhas financeiras pessoais que podem não estar alinhadas com as agendas burocráticas. A União de Poupanças e Investimentos da UE pretende mudar isso, criando mecanismos para empurrar o capital privado para sectores aprovados pelo governo.
A Comissão Europeia estima que os cidadãos da UE detenham 10 biliões de euros em poupanças inactivas, e pretende mobilizar esse dinheiro para financiar a militarização da Europa e apoiar o complexo militar-industrial europeu. A Comissária Europeia para os Serviços Financeiros e para a União de Poupança e Investimento, Maria Luís Albuquerque, afirmou explicitamente que o rearmamento europeu dependerá fortemente da captação de investimento privado.
Como Isto Será Feito?
- Taxas de juro negativas — A erosão lenta das poupanças, tornando oneroso manter dinheiro no banco.
- Investimentos forçados em sectores “verdes”, militares e “estratégicos” — O seu dinheiro pode não ir para onde quer, mas para onde os políticos decidem.
- Controlos de capital — Impedindo a livre movimentação do seu dinheiro para alternativas mais seguras.
Albuquerque declarou que o problema da Europa é a diferença entre poupanças paradas e empresas que precisam de financiamento. Para fechar essa diferença, a Comissão Europeia pretende criar um novo esquema para mobilizar fundos privados para o investimento na indústria da UE no âmbito da União de Investimento e Poupança.
Isto não tem a ver com liberdade económica. Tem a ver com direccionar capital para onde o Estado deseja. E o novo euro digital do BCE, a CBDC europeia, facilita ainda mais esse controlo.
O Euro Digital: A Ferramenta Perfeita de Controlo
Com o euro digital, o BCE está a introduzir dinheiro programável, o que significa que as transacções podem ser controladas, monitorizadas e até restringidas em tempo real.
O Que Pode Fazer o Dinheiro Programável?
- Aplicar taxas de juro negativas automaticamente — As suas poupanças digitais podem diminuir com o tempo.
- Restringir como e onde pode gastar — Compras podem ser bloqueadas para itens considerados “não essenciais”.
- Definir datas de validade para o dinheiro — Forçando-o a gastar rapidamente.
- Limitar levantamentos ou transferências — Impedindo-o de sair do sistema.
O BCE afirma que o euro digital melhorará a “eficiência financeira”, mas o seu verdadeiro poder reside em vigiar e controlar todas as transacções. Se você não pode manter dinheiro fora do sistema, então não é dono do seu dinheiro — o Estado é.
Como Proteger-se
Com a UE a apertar o cerco, precisa de agir agora para proteger a sua riqueza:
- Opte pelo Bitcoin — A melhor reserva de valor fora do controlo governamental.
- Use dinheiro físico enquanto pode — Mantenha-o em circulação para retardar a sua eliminação.
- Auto-custódia de tudo — Se não tem controlo directo, não é realmente seu.
- Eduque-se e resista — Espalhe a consciência antes que estas medidas se tornem irreversíveis.
Conclusão: Reivindique a Sua Liberdade Financeira
O plano da UE é claro: controlo total sobre o seu dinheiro e a sua vida.
O euro digital, as taxas de juro negativas e os controlos de capital não visam a prosperidade, mas garantir que ninguém possa escapar.
Mas Bitcoin oferece uma alternativa. Um sistema financeiro paralelo, incensurável, inconfiscável e deflacionário.
A escolha é clara: submeter-se à tirania financeira ou optar pela soberania monetária com Bitcoin.
O tempo para agir é agora.
Photo by Etienne Girardet on Unsplash
-
 @ 97c70a44:ad98e322
2025-03-06 18:38:10
@ 97c70a44:ad98e322
2025-03-06 18:38:10When developing on nostr, normally it's enough to read the NIP related to a given feature you want to build to know what has to be done. But there are some aspects of nostr development that aren't so straightforward because they depend less on specific data formats than on how different concepts are combined.
An example of this is how for a while it was considered best practice to re-publish notes when replying to them. This practice emerged before the outbox model gained traction, and was a hacky way of attempting to ensure relays had the full context required for a given note. Over time though, pubkey hints emerged as a better way to ensure other clients could find required context.
Another one of these things is "relay-based groups", or as I prefer to call it "relays-as-groups" (RAG). Such a thing doesn't really exist - there's no spec for it (although some aspects of the concept are included in NIP 29), but at the same time there are two concrete implementations (Flotilla and Chachi) which leverage several different NIPs in order to create a cohesive system for groups on nostr.
This composability is one of the neat qualities of nostr. Not only would it be unhelpful to specify how different parts of the protocol should work together, it would be impossible because of the number of possible combinations possible just from applying a little bit of common sense to the NIPs repo. No one said it was ok to put
ttags on akind 0. But no one's stopping you! And the semantics are basically self-evident if you understand its component parts.So, instead of writing a NIP that sets relay-based groups in stone, I'm writing this guide in order to document how I've combined different parts of the nostr protocol to create a compelling architecture for groups.
Relays
Relays already have a canonical identity, which is the relay's url. Events posted to a relay can be thought of as "posted to that group". This means that every relay is already a group. All nostr notes have already been posted to one or more groups.
One common objection to this structure is that identifying a group with a relay means that groups are dependent on the relay to continue hosting the group. In normal broadcast nostr (which forms organic permissionless groups based on user-centric social clustering), this is a very bad thing, because hosts are orthogonal to group identity. Communities are completely different. Communities actually need someone to enforce community boundaries, implement moderation, etc. Reliance on a host is a feature, not a bug (in contrast to NIP 29 groups, which tend to co-locate many groups on a single host, relays-as-groups tends to encourage one group, one host).
This doesn't mean that federation, mirrors, and migration can't be accomplished. In a sense, leaving this on the social layer is a good thing, because it adds friction to the dissolution/forking of a group. But the door is wide open to protocol additions to support those use cases for relay-based groups. One possible approach would be to follow this draft PR which specified a "federation" event relays could publish on their own behalf.
Relay keys
This draft PR to NIP 11 specifies a
selffield which represents the relay's identity. Using this, relays can publish events on their own behalf. Currently, thepubkeyfield sort of does the same thing, but is overloaded as a contact field for the owner of the relay.AUTH
Relays can control access using NIP 42 AUTH. There are any number of modes a relay can operate in:
-
No auth, fully public - anyone can read/write to the group.
-
Relays may enforce broad or granular access controls with AUTH.
Relays may deny EVENTs or REQs depending on user identity. Messages returned in AUTH, CLOSED, or OK messages should be human readable. It's crucial that clients show these error messages to users. Here's how Flotilla handles failed AUTH and denied event publishing:
LIMITS could also be used in theory to help clients adapt their interface depending on user abilities and relay policy.
- AUTH with implicit access controls.
In this mode, relays may exclude matching events from REQs if the user does not have permission to view them. This can be useful for multi-use relays that host hidden rooms. This mode should be used with caution, because it can result in confusion for the end user.
See Triflector for a relay implementation that supports some of these auth policies.
Invite codes
If a user doesn't have access to a relay, they can request access using this draft NIP. This is true whether access has been explicitly or implicitly denied (although users will have to know that they should use an invite code to request access).
The above referenced NIP also contains a mechanism for users to request an invite code that they can share with other users.
The policy for these invite codes is entirely up to the relay. They may be single-use, multi-use, or require additional verification. Additional requirements can be communicated to the user in the OK message, for example directions to visit an external URL to register.
See Triflector for a relay implementation that supports invite codes.
Content
Any kind of event can be published to a relay being treated as a group, unless rejected by the relay implementation. In particular, NIP 7D was added to support basic threads, and NIP C7 for chat messages.
Since which relay an event came from determines which group it was posted to, clients need to have a mechanism for keeping track of which relay they received an event from, and should not broadcast events to other relays (unless intending to cross-post the content).
Rooms
Rooms follow NIP 29. I wish NIP 29 wasn't called "relay based groups", which is very confusing when talking about "relays as groups". It's much better to think of them as sub-groups, or as Flotilla calls them, "rooms".
Rooms have two modes - managed and unmanaged. Managed rooms follow all the rules laid out in NIP 29 about metadata published by the relay and user membership. In either case, rooms are represented by a random room id, and are posted to by including the id in an event's
htag. This allows rooms to switch between managed and unmanaged modes without losing any content.Managed room names come from
kind 39000room meta events, but unmanaged rooms don't have these. Instead, room names should come from members' NIP 51kind 10009membership lists. Tags on these lists should look like this:["group", "groupid", "wss://group.example.com", "Cat lovers"]. If no name can be found for the room (i.e., there aren't any members), the room should be ignored by clients.Rooms present a difficulty for publishing to the relay as a whole, since content with an
htag can't be excluded from requests. Currently, relay-wide posts are h-tagged with_which works for "group" clients, but not more generally. I'm not sure how to solve this other than to ask relays to support negative filters.Cross-posting
The simplest way to cross-post content from one group (or room) to another, is to quote the original note in whatever event kind is appropriate. For example, a blog post might be quoted in a
kind 9to be cross-posted to chat, or in akind 11to be cross-posted to a thread.kind 16reposts can be used the same way if the reader's client renders reposts.Posting the original event to multiple relays-as-groups is trivial, since all you have to do is send the event to the relay. Posting to multiple rooms simultaneously by appending multiple
htags is however not recommended, since group relays/clients are incentivised to protect themselves from spam by rejecting events with multiplehtags (similar to how events with multiplettags are sometimes rejected).Privacy
Currently, it's recommended to include a NIP 70
-tag on content posted to relays-as-groups to discourage replication of relay-specific content across the network.Another slightly stronger approach would be for group relays to strip signatures in order to make events invalid (or at least deniable). For this approach to work, users would have to be able to signal that they trust relays to be honest. We could also use ZkSNARKS to validate signatures in bulk.
In any case, group posts should not be considered "private" in the same way E2EE groups might be. Relays-as-groups should be considered a good fit for low-stakes groups with many members (since trust deteriorates quickly as more people get involved).
Membership
There is currently no canonical member list published by relays (except for NIP 29 managed rooms). Instead, users keep track of their own relay and room memberships using
kind 10009lists. Relay-level memberships are represented by anrtag containing the relay url, and room-level memberships are represented using agrouptag.Users can choose to advertise their membership in a RAG by using unencrypted tags, or they may keep their membership private by using encrypted tags. Advertised memberships are useful for helping people find groups based on their social graph:

User memberships should not be trusted, since they can be published unilaterally by anyone, regardless of actual access. Possible improvements in this area would be the ability to provide proof of access:
- Relays could publish member lists (although this would sacrifice member privacy)
- Relays could support a new command that allows querying a particular member's access status
- Relays could provide a proof to the member that they could then choose to publish or not
Moderation
There are two parts to moderation: reporting and taking action based on these reports.
Reporting is already covered by NIP 56. Clients should be careful about encouraging users to post reports for illegal content under their own identity, since that can itself be illegal. Relays also should not serve reports to users, since that can be used to find rather than address objectionable content.
Reports are only one mechanism for flagging objectionable content. Relay operators and administrators can use whatever heuristics they like to identify and address objectionable content. This might be via automated policies that auto-ban based on reports from high-reputation people, a client that implements NIP 86 relay management API, or by some other admin interface.
There's currently no way for moderators of a given relay to be advertised, or for a moderator's client to know that the user is a moderator (so that they can enable UI elements for in-app moderation). This could be addressed via NIP 11, LIMITS, or some other mechanism in the future.
General best practices
In general, it's very important when developing a client to assume that the relay has no special support for any of the above features, instead treating all of this stuff as progressive enhancement.
For example, if a user enters an invite code, go ahead and send it to the relay using a
kind 28934event. If it's rejected, you know that it didn't work. But if it's accepted, you don't know that it worked - you only know that the relay allowed the user to publish that event. This is helpful, becaues it may imply that the user does indeed have access to the relay. But additional probing may be needed, and reliance on error messages down the road when something else fails unexpectedly is indispensable.This paradigm may drive some engineers nuts, because it's basically equivalent to coding your clients to reverse-engineer relay support for every feature you want to use. But this is true of nostr as a whole - anyone can put whatever weird stuff in an event and sign it. Clients have to be extremely compliant with Postell's law - doing their absolute best to accept whatever weird data or behavior shows up and handle failure in any situation. Sure, it's annoying, but it's the cost of permissionless development. What it gets us is a completely open-ended protocol, in which anything can be built, and in which every solution is tested by the market.
-
-
 @ 1c9dcd8f:1852f704
2024-08-13 07:34:46
@ 1c9dcd8f:1852f704
2024-08-13 07:34:46It is especially dangerous to be out late on the last night of November, for it is the closing scene of the revels—the last night when the dead have leave to dance on the hill with the fairies, and after that they must all go back to their graves and lie in the chill, cold earth, without music or wine till the next November comes round, when they all spring up again in their shrouds and rush out into the moonlight with mad laughter.
One November night, a woman of Shark Island, coming home late at the hour of the dead, grew tired and sat down to rest, when presently a young man came up and talked to her.
“Wait a bit,” he said, “and you will see the most beautiful dancing you ever looked on there by the side of the hill.”
And she looked at him steadily. He was very pale, and seemed sad.
“Why are you so sad?” she asked, “and as pale as if you were dead?”
“Look well at me,” he answered. “Do you not know me?”
“Yes, I know you now,” she said. “You are young Brien that was drowned last year when out fishing. What are you here for?”
“Look,” he said, “at the side of the hill and you will see why I am here.”
And she looked, and saw a great company dancing to sweet music; and amongst them were all the dead who had died as long as she could remember—men, women, and children, all in white, and their faces were pale as the moonlight.
“Now,” said the young man, “run for your life; for if once the fairies bring you into the dance you will never be able to leave them any more.”
But while they were talking, the fairies came up and danced round her in a circle, joining their hands. And she fell to the ground in a faint, and knew no more till she woke up in the morning in her own bed at home. And they all saw that her face was pale as the dead, and they knew that she had got the fairy-stroke. So the herb doctor was sent for, and every measure tried to save her, but without avail, for just as the moon rose that night, soft, low music was heard round the house, and when they looked at the woman she was dead.
It is a custom amongst the people, when throwing away water at night, to cry out in a loud voice, “Take care of the water;” or, literally from the Irish, “Away with yourself from the water”—for they say the spirits of the dead last buried are then wandering about, and it would be dangerous if the water fell on them.
One dark winter’s night a woman suddenly threw out a pail of boiling water without thinking of the warning words. Instantly a cry was heard as of a person in pain, but no one was seen. However, the next night a black lamb entered the house, having the back all fresh scalded, and it lay down moaning by the hearth and died. Then they all knew this was the spirit that had been scalded by the woman. And they carried the dead lamb out reverently and buried it deep in the earth. Yet every night at the same hour it walked again into the house and lay down and moaned and died. And after this had happened many times, the priest was sent for, and finally, by the strength of his exorcism, the spirit of the dead was laid to rest, and the black lamb appeared no more. Neither was the body of the dead lamb found in the grave when they searched for it, though it had been laid by their own hands deep in the earth and covered with the clay.
Before an accident happens to a boat, or a death by drowning, low music is often heard, as if under the water, along with harmonious lamentations, and then every one in the boat knows that some young man or beautiful young girl is wanted by the fairies, and is doomed to die. The best safeguard is to have music and singing in the boat, for the fairies are so enamoured of the mortal voices and music that they forget to weave the spell till the fatal moment has passed, and then all in the boat are safe from harm.
-
 @ 6e0ea5d6:0327f353
2025-02-21 18:15:52
@ 6e0ea5d6:0327f353
2025-02-21 18:15:52"Malcolm Forbes recounts that a lady, wearing a faded cotton dress, and her husband, dressed in an old handmade suit, stepped off a train in Boston, USA, and timidly made their way to the office of the president of Harvard University. They had come from Palo Alto, California, and had not scheduled an appointment. The secretary, at a glance, thought that those two, looking like country bumpkins, had no business at Harvard.
— We want to speak with the president — the man said in a low voice.
— He will be busy all day — the secretary replied curtly.
— We will wait.
The secretary ignored them for hours, hoping the couple would finally give up and leave. But they stayed there, and the secretary, somewhat frustrated, decided to bother the president, although she hated doing that.
— If you speak with them for just a few minutes, maybe they will decide to go away — she said.
The president sighed in irritation but agreed. Someone of his importance did not have time to meet people like that, but he hated faded dresses and tattered suits in his office. With a stern face, he went to the couple.
— We had a son who studied at Harvard for a year — the woman said. — He loved Harvard and was very happy here, but a year ago he died in an accident, and we would like to erect a monument in his honor somewhere on campus.— My lady — said the president rudely —, we cannot erect a statue for every person who studied at Harvard and died; if we did, this place would look like a cemetery.
— Oh, no — the lady quickly replied. — We do not want to erect a statue. We would like to donate a building to Harvard.
The president looked at the woman's faded dress and her husband's old suit and exclaimed:
— A building! Do you have even the faintest idea of how much a building costs? We have more than seven and a half million dollars' worth of buildings here at Harvard.
The lady was silent for a moment, then said to her husband:
— If that’s all it costs to found a university, why don’t we have our own?
The husband agreed.
The couple, Leland Stanford, stood up and left, leaving the president confused. Traveling back to Palo Alto, California, they established there Stanford University, the second-largest in the world, in honor of their son, a former Harvard student."
Text extracted from: "Mileumlivros - Stories that Teach Values."
Thank you for reading, my friend! If this message helped you in any way, consider leaving your glass “🥃” as a token of appreciation.
A toast to our family!
-
 @ 502ab02a:a2860397
2025-05-20 01:22:31
@ 502ab02a:a2860397
2025-05-20 01:22:31พอพูดถึงบริษัทอย่าง Formo ที่ทำชีสโดยไม่ใช้วัวเลย คนส่วนใหญ่จะนึกถึงคำว่า “นวัตกรรม” “ยั่งยืน” “ลดโลกร้อน” กันเป็นด่านแรก แต่พอเฮียมองทะลุม่านควันพวกนี้ไป จะเห็นทุนรายใหญ่ที่หนุนหลังอยู่ ซึ่งหลายเจ้าก็ไม่ใช่ผู้พิทักษ์โลก แต่เป็นผู้เล่นตัวจี๊ดในอุตสาหกรรมอาหารโลกมายาวนาน
หนึ่งในนั้นคือบริษัทจากเกาหลีใต้ชื่อ CJ CheilJedang ซึ่งอาจฟังดูไกลตัว แต่จริงๆ แล้ว เฮียว่าชื่อนี้โผล่ตามซองอาหารสำเร็จรูปในครัวคนไทยหลายบ้านโดยไม่รู้ตัว
ถ้าจะเข้าใจ Formo ให้ถึงแก่น เราต้องมองไปถึงทุนที่ “ใส่เงิน” และ “ใส่จุดยืน” ลงไปในบริษัทนั้น และหนึ่งในผู้ถือหุ้นรายสำคัญก็คือ CJ CheilJedang บริษัทเกาหลีใต้ที่ก่อตั้งมาตั้งแต่ปี 1953 โดยเริ่มจากการเป็นโรงงานผลิตน้ำตาล จากนั้นก็กินรวบแทบทุกวงจรอาหารของเกาหลี
โปรไฟล์ CJ แค่เห็นภาพรวมก็ขนลุกแล้วครับ ลูกพี่เราแข็งแกร่งขนาดไหน - เป็นเจ้าของแบรนด์ Bibigo ที่เราอาจจะคุ้นในสินค้า กิมจิ และ CJ Foods ที่มีขายทั่วโลก -เป็นผู้ผลิต กรดอะมิโน รายใหญ่ของโลก เช่น ไลซีน, ทรีโอนีน, ทริปโตแฟน ที่ใช้เป็นวัตถุดิบในอาหารสัตว์ แต่ตอนนี้หลายบริษัทเอาไปใส่ใน Plant-based food แล้วเคลมว่าเป็นโปรตีนสมบูรณ์ -เป็นเจ้าของโรงงานผลิต แบคทีเรียสายพันธุ์พิเศษ สำหรับการหมักหลายประเภท -ขึ้นชื่อเรื่อง bioscience โดยเฉพาะ precision fermentation ซึ่งเป็นเทคโนโลยีเดียวกับที่ Formo ใช้ผลิตเคซีน (โปรตีนในนมวัว)
แปลว่า CJ ไม่ได้มาลงทุนใน Formo แบบ “หวังผลกำไรเฉยๆ” แต่เขามองเห็น “อนาคตใหม่ของอาหาร” ที่ตัวเองจะเป็นเจ้าของต้นน้ำยันปลายน้ำ
คำถามก็คือเบื้องลึกการลงทุนใน Formo ใครได้อะไร? Formo ปิดรอบระดมทุน Series A ได้ประมาณ 50 ล้านดอลลาร์สหรัฐ เมื่อปี 2021 โดยมีนักลงทุนหลายเจ้า เช่น EQT Ventures, Elevat3 Capital, Atomico แต่ CJ CheilJedang ก็เป็นหนึ่งในผู้ลงทุนเชิงกลยุทธ์ (strategic investor) ที่เข้ามาแบบไม่ใช่แค่ลงเงิน แต่เอา เทคโนโลยี + เครือข่ายโรงงาน + ซัพพลายเชนระดับโลก มาเสริมให้ Formo ขยายได้เร็วขึ้น
การจับมือกันครั้งนี้มีนัยยะสำคัญครับ -Formo ได้ เทคโนโลยีหมักจุลินทรีย์ (ที่ CJ ถนัดมาก) และช่องทางกระจายสินค้าในเอเชีย -CJ ได้ ถือหุ้นในบริษัทที่กำลังจะเปลี่ยนภาพ “ผลิตภัณฑ์จากนม” ให้กลายเป็นสิ่งที่ไม่ต้องมีสัตว์อีกต่อไป ซึ่งจะเป็นกลยุทธ์สำคัญในการสร้างแบรนด์อาหารแห่งอนาคต ที่นมจะต้องมาจากโรงงานผลิตเท่านั้นจึงจะมีคุณสมบัติที่ดีทั้งสารอาหารและความสะอาด
CJ เองก็เคยประกาศต่อสื่อว่า อยากเป็น “Global Lifestyle Company” ซึ่งฟังดูเบาๆ แต่จริงๆ คือแผนใหญ่ในการ เปลี่ยนวิธีการกินของคนทั้งโลกได้เลยเช่นกัน -จาก “อาหารจริง” ไปเป็น “อาหารสังเคราะห์” (synthetic food) -จาก “ฟาร์มสัตว์” ไปเป็น “ถังหมักจุลินทรีย์” -จาก “ความหลากหลายตามธรรมชาติ” ไปเป็น “สูตรกลาง” ที่ควบคุมได้ในระดับโมเลกุล
การหนุนหลัง Formo จึงไม่ใช่เรื่องบังเอิญ แต่เป็นอีกหนึ่งหมากในกระดานใหญ่ที่ CJ วางไว้ เพื่อเป็นเจ้าของอาหารอนาคตแบบไม่ต้องเลี้ยงหมู ไก่ วัว แต่ครองเทคโนโลยีแทน
คำถามคือแล้วผู้บริโภคจะรู้ทันไหมว่า เบื้องหลังชีสที่ไม่มีวัว อาจมี “ทุนที่อยากครองโลกอาหาร” คำที่เคลมว่า “ยั่งยืน” อาจสร้างระบบอาหารใหม่ที่ยิ่งห่างจากธรรมชาติเข้าไปทุกที
คนที่เคย “กลัวสารเคมี” ในอาหารแปรรูป กลับกลืนผลิตภัณฑ์จากห้องแล็บ โดยคิดว่า “มันคือความสะอาดและอนาคต” #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 0fa80bd3:ea7325de
2025-02-14 23:24:37
@ 0fa80bd3:ea7325de
2025-02-14 23:24:37intro
The Russian state made me a Bitcoiner. In 1991, it devalued my grandmother's hard-earned savings. She worked tirelessly in the kitchen of a dining car on the Moscow–Warsaw route. Everything she had saved for my sister and me to attend university vanished overnight. This story is similar to what many experienced, including Wences Casares. The pain and injustice of that time became my first lessons about the fragility of systems and the value of genuine, incorruptible assets, forever changing my perception of money and my trust in government promises.
In 2014, I was living in Moscow, running a trading business, and frequently traveling to China. One day, I learned about the Cypriot banking crisis and the possibility of moving money through some strange thing called Bitcoin. At the time, I didn’t give it much thought. Returning to the idea six months later, as a business-oriented geek, I eagerly began studying the topic and soon dove into it seriously.
I spent half a year reading articles on a local online journal, BitNovosti, actively participating in discussions, and eventually joined the editorial team as a translator. That’s how I learned about whitepapers, decentralization, mining, cryptographic keys, and colored coins. About Satoshi Nakamoto, Silk Road, Mt. Gox, and BitcoinTalk. Over time, I befriended the journal’s owner and, leveraging my management experience, later became an editor. I was drawn to the crypto-anarchist stance and commitment to decentralization principles. We wrote about the economic, historical, and social preconditions for Bitcoin’s emergence, and it was during this time that I fully embraced the idea.
It got to the point where I sold my apartment and, during the market's downturn, bought 50 bitcoins, just after the peak price of $1,200 per coin. That marked the beginning of my first crypto winter. As an editor, I organized workflows, managed translators, developed a YouTube channel, and attended conferences in Russia and Ukraine. That’s how I learned about Wences Casares and even wrote a piece about him. I also met Mikhail Chobanyan (Ukrainian exchange Kuna), Alexander Ivanov (Waves project), Konstantin Lomashuk (Lido project), and, of course, Vitalik Buterin. It was a time of complete immersion, 24/7, and boundless hope.
After moving to the United States, I expected the industry to grow rapidly, attended events, but the introduction of BitLicense froze the industry for eight years. By 2017, it became clear that the industry was shifting toward gambling and creating tokens for the sake of tokens. I dismissed this idea as unsustainable. Then came a new crypto spring with the hype around beautiful NFTs – CryptoPunks and apes.
I made another attempt – we worked on a series called Digital Nomad Country Club, aimed at creating a global project. The proceeds from selling images were intended to fund the development of business tools for people worldwide. However, internal disagreements within the team prevented us from completing the project.
With Trump’s arrival in 2025, hope was reignited. I decided that it was time to create a project that society desperately needed. As someone passionate about history, I understood that destroying what exists was not the solution, but leaving everything as it was also felt unacceptable. You can’t destroy the system, as the fiery crypto-anarchist voices claimed.
With an analytical mindset (IQ 130) and a deep understanding of the freest societies, I realized what was missing—not only in Russia or the United States but globally—a Bitcoin-native system for tracking debts and financial interactions. This could return control of money to ordinary people and create horizontal connections parallel to state systems. My goal was to create, if not a Bitcoin killer app, then at least to lay its foundation.
At the inauguration event in New York, I rediscovered the Nostr project. I realized it was not only technologically simple and already quite popular but also perfectly aligned with my vision. For the past month and a half, using insights and experience gained since 2014, I’ve been working full-time on this project.
-
 @ c0a57a12:8b230f7a
2024-08-13 05:33:48
@ c0a57a12:8b230f7a
2024-08-13 05:33:48Concept:
This sauce is intended to be used on 10-16 lb smoked pork butt (Boston Butt). #foodstr
Ingredients:
- 1 Pineapple (cored, peeled)
- 2 cup coconut water
- 1/3 cup Red Wine Vinegar
- 6 Scotch Bonnet Peppers or 3 TBSP Eaton's Scotch Bonnet Pepper Sauce
- 4 tbsp minced garlic
- 4 tbsp minced onion
- 4 tbsp ground allspice
- 2 tbsp ground cinnamon
- 1 tbsp ground clove
- 1 tbsp ground nutmeg
- 1 tbsp dried thyme
- 2 tsp paprika
- 2 tsp ground ginger
- 1 tbsp salt
Instructions:
- Core pineapple
- Place all ingredients in blender. Blend well.
- Pour purée into medium saucepan
- Reduce to thicken.
- Allow sauce to cool.
-
 @ bf47c19e:c3d2573b
2025-05-24 16:13:51
@ bf47c19e:c3d2573b
2025-05-24 16:13:51Originalni tekst na bitcoin-balkan.com.
Pregled sadržaja
- Definisanje novca
- Šta je sredstvo razmene?
- Šta je obračunska jedinica?
- Šta je zaliha vrednosti?
- Zašto su važne funkcije novca?
- Novac Gubi Funkciju: Alhemičar iz Njutonije
- Eksploatacija pomoću Novca: Agri Perle
- Novac Gubi Funkciju 2. Deo: Kejnslandski Bankar
- Da li nas novac danas eksploatiše?
- Šta je novac, i zašto trebate da brinete?
- Efikasnija Ušteda Novca
- Zasluge
- Molim vas da šerujete!
Google izveštava o stalnom povećanju interesa u svetu za pitanje „Šta je novac?“ koji se postavlja iz godine u godinu, od 2004. do 2021., a sa naglim porastom nakon finansijske krize 2008. godine.
I izgleda se da niko nema dobar odgovor za to.
 Godišnji proseci mesečnih interesa za pretragu. 100 predstavlja najveći interes za pretragu tokom čitavog perioda, koji se dogodio u decembru 2019. Podaci sa Google Trends-a.
Godišnji proseci mesečnih interesa za pretragu. 100 predstavlja najveći interes za pretragu tokom čitavog perioda, koji se dogodio u decembru 2019. Podaci sa Google Trends-a.Međutim, odgovaranje na ovo naizgled jednostavno pitanje pomoći će vam da razjasnite ulogu novca u vašem životu. Jednom kada shvatite kako novac funkcioniše, tačno ćete videti i zašto svet danas ludi – i šta učiniti povodom toga. Zato hajde da se udubimo u to.
Na pitanje šta je novac, većina ljudi otvori svoje novčanike i pokaže nekoliko novčanica – “evo, ovo je novac!”
Ali po čemu se ove novčanice razlikuju od stranica vaše omiljene knjige? Pa, naravno, zavod za izradu novčanica te zemlje je odštampao te novčanice iz vašeg novčanika kako bi se oduprla falsifikovanju, i svi ih koriste da bi kupili odredjene stvari.
Međutim, Nemačka Marka imala je sva ova svojstva u prošlosti – ali preduzeća danas ne prihvataju te novčanice. Zapravo, građani Nemačke su početkom dvadesetih godina prošlog veka spaljivali papirne Marke kako bi grejali svoje domove. Marka je imala veću vrednost kao papir za potpalu nego kao novac!

1923. nemačka valuta poznata kao Marka bila je jeftinija od uglja i drveta!
Pa šta to čini novac, novcem?
Ispostavilo se da ovo nije pitanje na koje je lako dati odgovor.
Definisanje novca
Novac nije fizička stvar poput novčanice dolara. Novac je društveni sistem koji koristimo da bismo olakšali trgovinu robom i uslugama. Međutim, tokom istorije fizička monetarna dobra igrala su ključnu ulogu u društvenom sistemu novca, često kao znakovi koji predstavljaju vrednost u monetarnom sistemu. Ovaj sistem ima tri funkcije: 1) Sredstvo Razmene, 2) Obračunsku Jedinicu i 3) Zalihu Vrednosti.
Odakle dolaze ove funkcije, i zašto su one vredne?
Šta je sredstvo razmene?
Sredstvo razmene je neko dobro koje se obično razmenjuje za drugo dobro. Najčešće objašnjenje za to kako su se pojavila sredstva razmene glasi otprilike ovako: Boris ima ječam i želeo bi da kupi ovcu od Marka. Marko ima ovce, ali želi samo piliće. Ana ima piliće, ali ona ne želi ječam ili ovce.
To se naziva problem sticaja potreba: dve strane moraju da žele ono što druga ima da bi mogle da trguju. Ako se želje dve osobe ne podudaraju, oni moraju da pronađu druge ljude sa kojima će trgovati dok svi ne pronađu dobro koje žele.
 Ljudi koji trguju robom i uslugama moraju da imaju potrebe koje se podudaraju.
Ljudi koji trguju robom i uslugama moraju da imaju potrebe koje se podudaraju.Vremenom, veoma je verovatno da će se određena vrsta robe, poput pšenice, pojaviti kao sredstvo razmene jer su je mnogi ljudi želeli. Uzimajući pšenicu kao primer: pšenica je rešila “sticaje potreba” u mnogim zanatima, jer čak i ako onaj koji prima pšenicu a nije želeo da je koristi za sebe, znao je da će je neko drugi želeti.
Ovo nazivamo prodajnost imovine.
Pšenica je dobar primer dobra za prodaju jer svi moraju da jedu, a od pšenice se pravi hleb. Pšenica ima vrednost kao sastojak hleba i kao dobro koje olakšava trgovinu rešavanjem problema „sticaja potreba“.
Razmislite o svojoj želji da dobijete više novčanica u eurima ili drugoj valuti. Ne možete da jedete novčanice da biste preživeli, a i ne bi vam bile od velike koristi ako poželite da ih koristite kao građevinski materijal za vašu kuću. Međutim, znate da sa tim novčanicama možete da kupite hranu i kuću.
Stvarne fizičke novčanice su beskorisne za vas. Novčanice su vam dragocene samo zato što će ih drugi prihvatiti za stvari koje su vama korisne.
Tokom dugog perioda istorije, novac je evoluirao do te mere da monetarno dobro može imati vrednost, a da to dobro ne služi za bilo koju drugu ‘suštinsku’ upotrebu, poput hrane ili energije. Umesto toga, njegova upotreba je zaliha vrednosti i jednostavna zamena za drugu robu u bilo kom trenutku koji poželite.
Šta jedno dobro čini poželjnijim i prodajnijim od drugog dobra?
Deljivost
Definicija: Sposobnost podele dobra na manje količine.
Loš Primer: Dijamante je teško podeliti na manje komade. Za zajednicu od hiljada ljudi koji dnevno izvrše milione transakcija, dijamanti čine loše sredstvo razmene. Previše su retki i nedeljivi da bi se koristili za mnoge transakcije.
Ujednačenost
Definicija: Sličnost pojedinačnih jedinica odredjenog dobra.
Loš Primer: Krave nisu ujednačene – neke su veće, neke manje, neke bolesne, neke zdrave. Sa druge strane, unca čistog zlata je jednolična – jedna unca je potpuno ista kao sledeća. Ovo svojstvo se takođe često naziva zamenljivost.
Prenosivost
Definicija: Lakoća transporta dobra.
Loš Primer: Krava nije baš prenosiva. Zlatnici su prilično prenosivi. Papirne novčanice su još prenošljivije. Knjiga u kojoj se jednostavno beleži vlasništvo nad tim vrednostima (poput Rai kamenog sistema ili digitalnog bankovnog računa) je neverovatno prenosiva, jer nema fizičkog dobra koje treba nositi sa sobom za kupovinu. Postoji samo sistem za evidentiranje vlasništva nad tim vrednostima u nematerijalnom obliku.
Kako dobro postaje sredstvo razmene?
Dobra postaju, i ostaju sredstva razmene zbog svoje univerzalne potražnje, takođe poznate kao njihova prodajnost, čemu pomažu svojstva koja su gore nabrojana.
Mnogo različitih dobara mogu u različitoj meri delovati kao sredstva razmene u ekonomiji. Danas, naša globalna ekonomija koristi valute koje izdaju države, zlato, pa čak i robu poput nafte kao sredstvo razmene.
Šta je obračunska jedinica?
Stvari se komplikuju kada u ekonomiji postoji mnogo robe koja se prodaje. Čak i sa samo 5 dobara, postoji 10 “kurseva razmene” između svake robe kojih svi u ekonomiji moraju da se sete: 1 svinja se menja za 15 pilića, 1 pile se menja za 15 litara mleka, desetak jaja se menja za 15 litara mleka, i tako dalje. Ako ekonomija ima 50 dobara, među njima postoji 1.225 “kurseva razmene”!
Sredstvo za merenje vrednosti
Zamislite obračunsku jedinicu kao sredstvo za merenje vrednosti. Umesto da se sećamo vrednosti svakog dobra u poredjenju sa drugim dobrima, mi samo treba da se setimo vrednosti svakog dobra u poredjenju sa jednim dobrom – obračunskom jedinicom.
Umesto da se setimo 1.225 kurseva razmene kada imamo 50 proizvoda na tržištu, mi treba da zapamtimo samo 50 cena.
Na primer, ne treba da se sećamo da litar mleka vredi 1/15 piletine ili desetak jaja, možemo da se samo setimo da litar mleka košta 1USD.
Poređenje dobara je lakše sa obračunskom jedinicom
Obračunska jedinica takođe olakšava upoređivanje vrednosti i donošenje odluka. Zamislite da pokušavate da kupite par Nike Air Jordan patika kada ih jedan prodavac prodaje za jedno pile, a drugi za 50 klipova kukuruza.
Šta je zaliha vrednosti?
Do sada smo gledali samo primere transakcija koje se odvijaju u određenom trenutku u vremenu.
Međutim, ljudi vrše transakcije tokom vremena – oni štede novac i troše ga kasnije. Da bi odredjeno dobro moglo da funkcioniše pravilno kao monetarno dobro, ono treba da održi vrednost tokom vremena.
Novac koji vremenom dobro drži vrednost daje njegovom imaocu više izbora kada će taj novac da potroši.
To znači da prodajnost dobra uključuje njegovu sposobnost da održi vrednost tokom vremena.
Šta jedno dobro čini boljom zalihom vrednosti od drugog dobra?
Trajnost
Definicija: Sposobnost dobra da vremenom zadrži svoj oblik.
Loš Primer: Jagode čine lošu zalihu vrednosti jer se lako oštete i brzo trunu.
Odluka je daleko lakša ako jedan prodavac naplaćuje 150 USD, a drugi 200 USD – odmah je očigledno koja je bolja ponuda jer su vrednosti izražene u istoj jedinici.
Teške za Proizvodnju
Definicija: Teškoće koje ljudi imaju u proizvodnji veće količine dobra.
Loš Primer: Papirne novčanice predstavljaju lošu zalihu vrednosti jer banke i vlade mogu jeftino da ih naprave.
Sa zlatom je suprotno – u ponudi se nalazi ograničena količina uprkos velikoj potražnji za njim, jednostavno zato što ga je vrlo teško iskopati iz zemlje. Ova ograničena ponuda osigurava da svaka jedinica zlata održi vrednost tokom vremena.
Kako dobra postaju zalihe vrednosti?
Dobro postaje zaliha vrednosti ako se vremenom pokaže trajnim i teškim za proizvodnju.
Samo će vreme pokazati da li je neko dobro zaista trajno i da li ga je teško proizvesti. Zbog toga neki oblici novca su postojali vekovima pre nego što je neko otkrio način da ih proizvede više, i na kraju se to dobro više nije koristilo kao novac.
Ovo je priča o školjkama, Rai kamenju i mnogim drugim oblicima novca tokom istorije.
Zlato je primer dobra koje je hiljadama godina služilo kao dobra zaliha vrednosti. Zlato se ne razgrađuje tokom vremena i još uvek ga je teško proizvesti. Hiljadama godina alhemičari su bezuspešno pokušavali da sintetišu zlato iz jeftinih materijala.
Čak i sa današnjim naprednim rudarskim tehnikama, svake godine svi svetski rudnici zlata zajedno mogu da proizvedu samo 2% od ukupne ponude zlata u prometu.
Teškoće u proizvodnji zlata daju izuzetno visok odnos “zaliha i protoka”: zaliha je broj postojećih jedinica, a protok su nove jedinice stvorene tokom određenog vremenskog perioda. Svake godine se stvori vrlo malo novih jedinica zlata, iako je potražnja za zlatom obično vrlo velika.
Kombinujući ovo sa deljivošću, ujednačenošću i prenosivošću zlata, nije ni čudo što je zlato čovečanstvu služilo kao monetarno dobro tokom poslednjih 5.000 godina. Pošto je zlato teško proizvesti, možemo ga nazvati teškim novcem (hard money).
Kao rezultat toga, svoju vrednost je u velikoj meri zadržao kroz milenijume. Cena većine dobara i usluga u pogledu zlata zapravo se vremenom smanjivala kao rezultat tehnoloških inovacija, koje sve proizvode čine jeftinijim.
Uzmimo na primer cene hrane prema praćenju Kancelarije za hranu i poljoprivredu UN-a: sa obzirom na skokove u poljoprivrednoj tehnologiji tokom poslednjih 60 godina, cene hrane drastično su pale kada se procenjuju u zlatu. To čak i važi uprkos činjenici da obični ljudi retko koriste zlato za kupovinu stvari.
 Cene hrane su padale u pogledu zlata tokom proteklih 60 godina, i mnogo pre toga (FAO Indeks Cena Hrane u Zlatu)
Cene hrane su padale u pogledu zlata tokom proteklih 60 godina, i mnogo pre toga (FAO Indeks Cena Hrane u Zlatu)Zaliha vrednosti omogućava ljudima da uštede novac kako bi mogli da ga ulažu u pokretanje preduzeća i obrazovanje, povećavajući produktivnost društva.
Monetarna dobra koja dobro čuvaju vrednost takođe podstiču dugoročniji pogled na život, ili kratke vremenske preference. Pojedinac može da radi 10 godina, uštedi odredjeno monetarno dobro koje je dobra zaliha vrednosti, i nema potrebe da se plaši da će njegova ušteđevina biti izbrisana krahom tržišta ili povećanjem ponude tog dobra.
Zašto su važne funkcije novca?
Kada neki oblik novca izgubi bilo koju od svojih važnih funkcija kao što su sredstvo razmene, obračunska jedinica i zaliha vrednosti, celokupna ekonomija i društvo mogu da se rastrgnu.
Tokom istorije često vidimo grupe ljudi koje eksploatišu druge iskorišćavajući nesporazume o novcu i važnosti njegovih funkcija.
Sledeće, proći ću kroz istoriju novca, prvo hipotetički da bih ilustrovao poentu, a zatim ću preći na stvarne istorijske primere. Kroz ove primere videćemo štetne efekte na društva u slučajevima kada se izgubi samo jedna od tih ključnih funkcija novca.
Novac Gubi Funkciju: Alhemičar iz Njutonije
Kroz istoriju, mnoga dobra su dolazila i odlazila kao oblici novca. Na žalost, kada se neki oblik novca ukine, ponekad postoji grupa ljudi koja eksploatiše drugi oblik manipulišući tim novcem.
Hajde da pogledamo hipotetičko selo zvano Njutonija da bismo razumeli kako dolazi do ove eksploatacije.
Zelene perle postaju Novac
Tokom stotina godina ribolova u obližnjoj reci, stanovnici Njutonije sakupljali su zelene perle iz vode. Zrnca su mala, lagana, izdržljiva, jednolična i retko se pojavljuju u reci. Ljudi prvo priželjkuju perle zbog svoje lepote. Na kraju, seljani shvataju da svi drugi žele perle – one se vrlo lako mogu prodati. Zrnca uskoro postaju sredstvo razmene i obračunska jedinica u selu: pile je 5 zrna, vreća jabuka 2 zrna, krava 80 zrna.
Ukupna ponuda perli je prilično konstantna i cene se vremenom ne menjaju mnogo. Seoski starešina je uveren da može da se opustiti u poslednjim danima živeći od svoje velike zalihe perli.
Alhemičar stvara više perli
Seoski alhemičar je poželeo da bude bogat čovek, ali nije voleo da vredno radi na tome. Umesto da traži perle u reci ili da prodaje vrednu robu drugim seljanima, on sedeo je u svojoj laboratoriji. Na kraju je otkrio kako da lako stvori stotine perli sa malo peska i vatre.
Seljani koji su tragali za perlama u reci bili su srećni ako bi svaki dan pronašli po 1 zrno. Alhemičar je mogao da proizvede stotine uz malo napora.
Alhemičar troši svoje perle
Budući da je bio prilično zao, alhemičar nije svoj metod pravljenja zrna delio ni sa kim drugim. Stvorio je sebi još više perli i počeo da ih troši za dobra na tržištu u Njutoniji. Tokom sledećih meseci, alhemičar je kupio farmu pilića, nekoliko krava, finu svilu, posteljine i ogromno imanje. On je imao priliku da kupi ova dobra po normalnim cenama na tržištu.
Alhemičarevo trošenje ostavljalo je seljanima mnogo perli, ali malo njihove vredne robe.
Svi seljani su se osećali bogatima – imali su tone perli! Međutim, polako su primetili da i svi ostali takodje imaju tone.
Cene počinju da rastu
Uzgajivač pilića primetio je da sva roba koju je trebalo da kupi na pijaci poskupela. Džak jabuka sada se prodaje za 100 perli – 50 puta više od njihove cene pre nekoliko meseci!
Iako je sada imao hiljade perli, uskoro bi mogao da ostane bez njih zbog ovih cena. Pitao se – da li zaista može sebi da priušti da prodaje svoje piliće za samo 5 perli po komadu? Morao je i on da podigne svoje cene.
Jednostavno rečeno, kao rezultat alhemičarevog trošenja njegovih novostvorenih perli, bilo je previše perli koje su jurile premalo dobara – pa su cene porasle.
Kupci robe bili su spremni da potroše više perli da bi kupili potrebna dobra. Prodavci robe su trebali da naplate više da bi bili sigurni da su zaradili dovoljno da kupe potrebna dobra za sebe.
Budući da su cene svih dobara porasle, možemo reći da se vrednost svake perle smanjila.
Nejednakost bogatstva raste
Seoski starešina, koji je vredno radio da sačuva hiljade perli, sada se našao osiromašenim i gladnim. U međuvremenu, alhemičar je udobno sedeo na svom velikom imanju sa kravama, pilićima i slugama koji su se brinuli za svaki njegov hir.
Alhemičar je efikasno ukrao bogatstvo celog sela, tako što je jeftino proizvodio perle i koristio ih za kupovinu vredne robe.
Ono što je najvažnije, kupio je robu pre nego što je tržište shvatilo da je više perli u opticaju i da ima manje robe, što je dovelo do rasta cena. Ova dodatna proizvodnja perli nije dodala korisnu robu ili usluge selu.
Eksploatacija pomoću Novca: Agri Perle
Nažalost, priča o alhemičaru iz Njutonije nije u potpunosti hipotetička. Ovaj prenos bogatstva kroz stvaranje novca ima istorijske i moderne presedane.
Na primer, afrička plemena su nekada koristila staklene perle, poznate kao “agri perle”, kao sredstvo razmene. U to vreme plemenskim ljudima je bilo veoma teško da prave staklene perle, i one su predstavljale težak novac unutar njihovog plemenskog društva.
Niko nije mogao jeftino da proizvede perle i koristiti ih za kupovinu skupe, vredne robe poput kuća, hrane i odeće.
Sve se promenilo kada su stigli Evropljani, i primetili upotrebu staklenih perli kao novca.
U to vreme, Evropljani su mogli jeftino da stvaraju staklo u velikim količinama. Kao rezultat toga, Evropljani su počeli tajno da uvoze perle i koriste ih za kupovinu dobara, usluga i robova od Afrikanaca.
Vremenom se iz Afrike izvlačila vredna roba i ljudi, dok je plemenima ostajalo mnogo perli i malo robe.
Perle su izgubile veći deo vrednosti zbog inflacije uzrokovane snabdevanjem od strane Evropljana.
Rezultat je bio osiromašenje afričkih plemena i bogaćenje Evropljana, kako to ovde objašnjava monetarni istoričar Bezant Denier.
Dragocena roba je kupljena jeftino proizvedenim monetarnim dobrom.
Profitiranje na proizvodnji novca: Emisiona dobit
Ova priča ilustruje kako se bogatstvo prenosi kada jedna grupa može jeftino da proizvodi monetarno dobro.
Razlika između troškova proizvodnje monetarnog dobra i vrednosti tog monetarnog dobra poznata je kao emisiona dobit, eng. seignorage.
Kada je monetarno dobro mnogo vrednije od troškova proizvodnje, ljudi će proizvesti više od monetarnog dobra da bi uhvatili profit od emisione dobiti.
Na kraju će ova povećana ponuda dovesti do pada vrednosti monetarnog dobra. To je zbog zakona ponude i potražnje: kada se ponuda povećava, cena (poznata i kao vrednost) dobra opada.
Novac Gubi Funkciju 2. Deo: Kejnslandski Bankar
U priči o Njutoniji, alhemičar je otkrio način da se od malo peska jeftino stvori više zelenih perli. To se u stvarnosti odigralo kroz trgovinu između Evropljana i Afrikanaca, pričom o agri perlama. Međutim, ove priče su pomalo zastarele – mi više ne trgujemo robom za perle.
Da bismo nas doveli do modernog doba, hajde da promenimo neka imena u našoj priči:
- Selo Njutonija postaje država koja se zove Kejnsland
- Alhemičar postaje bankar
- Seoski starešina postaje penzioner
- Zelene perle postaju zlato, koje niko ne može jeftinije da stvori – čak ni bankar.
Bankar Menja Papirne Novčanice za Zlato
Kao i u stvarnosti, bankar u ovoj priči nema formulu ili trik da stvori više zlata. Međutim, bankar bezbedno čuva zlato u vlasništvu svakog građanina Kejnslanda. Bankar daje svakom građaninu po jednu potvrdu za svaku uncu zlata koje ima u svom trezoru.
Te potvrde se mogu iskoristiti u bilo koje vreme za stvarno zlato. Papirne potvrde ili novčanice su mnogo pogodnije za plaćanje nego nošenje zlata kroz supermarket.
Građani su srećni – oni imaju prikladno sredstvo plaćanja u vidu bankarevih novčanica, i znaju da niko ne može da ukrade njihovo bogatstvo falsifikujući više zlata.
Građani na kraju počinju da plaćaju u potpunosti papirnim novčanicama, ne trudeći se nikad da zamene svoje novčanice za zlato. Na kraju, novčanice postaju “dobre kao i zlato” – svaka predstavlja fiksnu količinu zlata u bankarevom trezoru.
Ukupno kruži 1.000.000 novčanica, od kojih je svaka otkupljiva za jednu uncu zlata. 1.000.000 unci zlata sedi u bankarevom trezoru. Svaka novčanica je u potpunosti podržana u zlatu.
Starešina koji je sačuvao sve svoje perle u priči o Njutoniji sada je penzioner u Kejnslandu, koji svoje zlato drži u banci i planira da ugodno živi od novčanica koje je dobio zauzvrat.
Hajde da u ovu priču dodamo i novi lik: premijera Kejnslanda. Premijer naplaćuje porez od građana i koristi ga za plaćanje javnih usluga poput policije i vojske. Premijer takođe drži vladino zlato kod bankara.
Bankar Menja Papirne Novčanice za Dug
Premijer želi da osigura da nacionalno zlato ostane na sigurnom, pa banku štiti policijom. Bankar i premijer se zbog toga zbližavaju, pa premijer traži uslugu. Traži od bankara da kreira 200.000 novčanica za premijera, uz obećanje da će mu premijer vratiti za pet godina. Premijeru su novčanice potrebne za finansiranje rata. Građani Kejnslanda borili su se protiv većih poreza zbog finansiranja rata, pa je morao da se obrati bankaru.
Bankar se slaže da izradi novčanice, ali pod jednim uslovom: bankar uzima deo od 10.000 novčanica za sebe. Premijer prihvata posao kojim bankar ’kupuje državni dug’. Sada je u opticaju 1.200.000 novčanica, potpomognutih kombinacijom 1.000.000 unci zlata i ugovorom o dugu sa vladom za 200.000 novčanica.
Premijer troši svoje nove novčanice na bombe kupujući ih od dobavljača iz domaće vojne industrije, a bankar sebi kupuje veliki luksuzni stan.
Dobavljač iz vojne industrije koristi sve nove novčanice koje je dobio od premijera da kupi amonijum nitrat (đubrivo koje se koristi u bombama) za proizvodnju bombi. Sve njegove kupovine povećavaju cenu đubriva za uzgajivače pšenice u Kejnslandu, pa oni podižu cenu pšenice.
Kao uzrok toga, pekar koji kupuje pšenicu treba da podigne cenu svog hleba da bi ostao u poslu. Na taj način cene u Kejnslandu počinju da rastu, baš kao što su to činile u Njutoniji kada su nove perle ušle u opticaj.
Papirne Novčanice Više Ne Predstavljaju Zlato
Penzioner nailazi na finansijski časopis u kojem se pominje premijerov dogovor da se zaduži za finansiranje rata. Obzirom da je mudar, on zna da bombe loše vraćaju ulaganje i sumnja da će premijer ikada da vrati svoj dug.
Ako on ‘podmiri’ svoj dug, to bi ostavilo 1.200.000 novčanica u opticaju sa samo 1.000.000 unci zlata da bi ih podržalo, obezvređujući njegovu ušteđevinu. Već oseća stisak u džepu zbog porasta cena, i on odlučuje da se uputi u lokalnu banku i preda svoje novčanice i zameni ih za zlato, koje niko ne može da napravi u većoj količini.
Kada penzioner stigne u banku, on zatiče i mnoge druge okupljene oko banke. Svi oni se nadaju da će uzeti zlato koje predstavljaju njihove novčanice. Građani Kejnslanda sa pravom se plaše da njihove novčanice gube na vrednosti – oni to već osećaju zbog porasta cena.
Vrata su zaključana, sa obaveštenjem bankara na njima:
Po nalogu premijera, onom koji se plaši za stabilnost ove bankarske institucije, ova banka više neće podržavati konvertibilnost papirnih novčanica u zlato. Hvala vam!
Gomila se razilazi, ostavljena sa jednim izborom: da zadrže svoje novčanice, koje sada vrede manje od 1 unce zlata. Građani sa dovoljno finansijske stabilnosti odlučuju da ulože svoje novčanice u kupovinu akcija banke i kompanija vojne industrije, koje dobro posluju jer mogu da kupuju stvari pre nego što se povećaju tržišne cene.
Mnogi ljudi nisu u mogućnosti da investiraju – oni moraju da gledaju kako njihove zarade stagniraju i kako njihova ušteđevina polako ali sigurno gubi vrednost.
Penzioner, koji se nadao da će živeti od novčanica koje je zaradio tokom svojih 40 radnih godina, sada 40 sati nedeljno provodi iza kase u lokalnoj prodavnici, pitajući se gde je sve pošlo po zlu.
Dug Nikada Nije Otplaćen
Prošlo je nekoliko godina, a premijerov dug prema banci dolazi na naplatu. Budući da je potrošio svih 200.000 novčanica na bombe, koje nemaju baš dobar povraćaj ulaganja, on nema novčanice koje može da vrati banci. Plus, premijer želi da kupi još bombi za svoj rat.
Bankar uverava premijera da je sve u redu. Bankar će napraviti novi ugovor o dugu za 600.000 novčanica, koji bi trebao da stigne na naplatu u narednih 5 godina. Premijer može da iskoristi 200.000 od tih novih 600.000 novčanica da vrati svoj prvobitni dug prema banci, zadrži još 300.000 da kupi još bombi i da 100.000 bankaru da bi mu platio njegove usluge.
To nastavlja da se dešava – svaki put kada dug dospeva na naplatu, bankar stvara više novčanica za vraćanje starijih dugova i daje premijeru još više novca za trošenje. Ovaj ciklus se nastavlja.
Šta se dešava u Kejnslandu?
- Oni koji prvi dobiju nove novčanice, gledaju kako se njihovo bogatstvo povećava
- To uključuje bankara, premijera, vladu i sve one koji mogu da pristupe mogućnostima za investiranje u preduzeća koja prva dobiju nove novčanice (finansijske, vojne itd.).
- Cene roba rastu
- Cene se ne povećavaju ravnomerno – one se povećavaju gde god nove novčanice prvo uđu u ekonomiju i od tog trenutka imaju efekat talasa na tržišta. U našem primeru prvo raste cena amonijum nitrata, zatim cena pšenice, pa cena hleba. A tek na kraju zarade običnih ljudi.
- Štednja i životni standard opšte populacije se smanjuju
- Najviše pate oni koji žive od plate do plate i ne mogu da ulažu. Čak i oni koji su u mogućnosti da investiraju podložni su hirovima tržišta. Mnogi su prisiljeni da prodaju svoje investicije po niskim cenama tokom pada tržišta samo da bi platili svoje dnevne potrebe.
- Razlika u prihodima i bogatstvu između bogatih i siromašnih se povećava
- Bogatstvo opšte populacije se smanjuje, dok se bogatstvo onih koji su blizu mesta gde se troše nove novčanice povećava. Rezultat je disparitet koji se vremenom samo proširuje.
Da li nas novac danas eksploatiše?
Priča o Njutoniji i stvarna priča o agri perlama u Africi deluju pomalo zastarelo. Priča o Kejnslandu, međutim, deluje neobično poznato. U našem svetu cene robe uvek rastu, i vidimo rekordne nivoe nejednakosti u bogatstvu.
U poslednjem odeljku ovog našeg članka Šta je novac, proći ću kroz nastanak bankarstva i korake koji su bili potrebni da se dođe do današnjeg sistema, gde banke i vlade sarađuju u kontroli ekonomije i samog novca.
Šta su banke, i odakle su one došle?
Pojava bankarstva verovatno se dogodila da bi olakšala poljoprivrednu trgovinu i da bi povećala pogodnosti. Iako su se mnoga društva na kraju konvergirala ka upotrebi zlata i srebra kao novca, ovi metali su bili teški i opasni za nošenje kao tovar. Međutim, u mnogim slučajevima ih nije ni trebalo prevoziti. Uzmite ovaj primer:
Grad treba da plati poljoprivrednicima na selu za žito, a poljoprivrednici gradskoj vojsci za zaštitu od varvara. U ovom dogovoru zlato se kreće u oba smera: prema poljoprivrednicima u selu kako bi im se platilo žito, i nazad u grad da bi se platila vojska. Da bi olakšali ove transakcije, preduzetnici su stvorili koncept banke. Banka je zlato čuvala u sigurnom trezoru i izdavala novčanice od papira. Svaka priznanica je predstavljala potvrdu da njen imaoc poseduje određenu količinu zlata u banci. Imaoc novčanice je u svako doba mogao da uzme svoje zlato nazad vraćanjem te novčanice banci.
Korisnici banke mogli su lakše da trguju sa novčanicama od papira, i onaj koji poseduje novčanice mogao je da preuzme njihovo fizičko zlato u bilo kom trenutku. To je te novčanice učinilo “dobrim kao i zlato”.
Banke su izdržavale svoje poslovanje naplaćujući od kupaca naknadu za skladištenje zlata ili pozajmljivanjem dela zlata i zaračunavanjem kamata na njega. Trgovina na ovaj način je mogla da se odvija sa laganim novčanicama od papira umesto sa teškim vrećama zlatnika.
Ovakva praksa sa transakcijama, korišćenjem papirne valute potpomognute monetarnim dobrima, verovatno je započela u Kini u 7. veku.
Na kraju se proširila Evropom 1600-ih, a svoj zalet dobila je u Holandiji sa bankama poput Amsterdamske Wisselbanke. Novčanice Wisselbank-e često su vredele više od zlata koje ih je podržavalo, zbog dodane vrednosti njihovih pogodnosti.
Uspon nacionalnih ‘centralnih banaka’
Tokom vekova, zlato je počelo da se sakuplja u trezorima banaka, jer su ljudi više voleli pogodnosti transakcija sa novčanicama.
Na kraju, nacionalne banke u vlasništvu vlada preuzele su ulogu čuvanja zlata od privatnih banaka koje su započeli preduzetnici.
Nacionalne papirne valute potpomognute zlatnim rezervama u nacionalnim bankama zamenile su novčanice iz privatnih banaka. Sve nacionalne valute bile su jednostavno potvrde za zlato koje se nalazilo u trezoru nacionalne banke.
Ovaj sistem je poznat kao zlatni standard – sve valute su jednostavno predstavljale različite težine zlata.
 U gornjem levom uglu novčanice možete videti da piše da je novčanica “zamenljiva za zlato”. Savremeni dolari nemaju ovaj natpis, ali inače izgledaju vrlo slično. Izvor
U gornjem levom uglu novčanice možete videti da piše da je novčanica “zamenljiva za zlato”. Savremeni dolari nemaju ovaj natpis, ali inače izgledaju vrlo slično. IzvorZlatni sistem je postojao veći deo vremena, sve do Prvog svetskog rata. Vladama je bilo teško da prikupe novac za ovaj rat putem poreza, pa su morale da budu kreativne.
Kada vlade troše više nego što zarađuju na porezima, to se naziva deficitna potrošnja.
Kako vlade mogu ovo da urade? Vlade to rade tako što pozajmljuju novac prodavajući svoj dug.
Tokom Prvog svetskog rata, vlade su građanima i preduzećima prodavale vrstu duga koja se naziva ratna obveznica. Kada građanin kupi ratnu obveznicu, on preda svoj novac vladi i dobije papir u kojem je stajalo vladino obećanje da će vlasniku obveznice vratiti novac, plus kamate, za nekoliko godina.
Plakat koji obaveštava građane, tražeći od njih da kupe ratne obveznice – što predstavlja zajam vladi. Izvor
Centralne banke ‘monetizuju’ državni dug
Međutim, građani i preduzeća nisu bili voljni da kupe dovoljno ratnih obveznica za finansiranje Prvog svetskog rata.
Vlade se nisu predale – pa su zatražile od svojih nacionalnih ‘centralnih banaka’ da one kupe ove obveznice. Centralne banke su otkupile obveznice, ali ih nisu platile valutom potpomognutom postojećim zlatnim rezervama, kao što su to činili građani i banke prilikom kupovine obveznica.
Centralne banke su umesto toga davale vladi novu, sveže štampanu papirnu valutu potpomognutu samo obveznicom. Ovu valutu podržalo je samo obećanje da će im vlada vratiti dugove. Ovo je poznato kao monetizacija duga.
Budući da su ratne obveznice i valuta samo komadi papira, one su lake i jeftine za proizvodnju i mogu se napraviti u ogromnim količinama. Ono što ograničava proizvodnju i jednog i drugog je poverenje.
Ima smisla da se neko rastane od svog teško stečenog novca da kupi državnu obveznicu, samo ako veruje da će vlada da vrati svoj dug, plus kamate. Centralna banka je “krajnji kupac”, što znači da će ona da kupi državne obveznice kada to niko drugi neće da uradi.
Zapamtite, centralnu banku gotovo da ništa ne košta da kupi državne obveznice, jer oni sami štampaju valutu da bi ih kupili.
Zamislite da pridjete najskupljem automobilu u autosalonu – koji košta 100.000 USD. Mislite da je automobil lep, ali taj novac biste radije potrošili na lepši stan – tako da ste spremni da platite samo 40.000 USD za taj auto.
Sada, hajde da zamislimo da imate štampač za novac i da vas košta samo 50 USD za mastilo i papir da bi ištampali 1.000.000 USD. Vi biste odmah kupili auto, čak i ako biste morali da se cenkate sa drugim čovekom, i da ga na kraju platite 150.000 USD!
Ista stvar se dešava kada centralna banka kupuje obveznice (dugove) od vlade. Centralna banka može da stvori valutu toliko jeftino, da su spremni da plate i više nego što bi drugi platili ove obveznice i nastaviće da ih kupuju čak i kada niko drugi ne bude želeo.
Monetizacija duga uzrokuje inflaciju
Kada centralne banke monetizuju državni dug, funkcija novca kao zalihe vrednosti počinje da se nagriza. Vlada troši novi novac koji je dobila od svoje centralne banke na ratnu robu, obroke i još mnogo toga.
Cene roba rastu od ove novoštampane valute koja kruži kroz ekonomiju. Kada se cene povećavaju, to znači da se vrednost svake jedinice valute smanjuje. Svi koji drže valutu sada imaju manje vrednosti. Danas to nazivamo sporim gubitkom funkcije zalihe vrednosti u novčanoj inflaciji.
Za Nemačku nakon Prvog svetskog rata monetizacija duga izazvala je totalni slom Nemačke ekonomije i stvorila uslove za rast fašizma.
Kao deo sporazuma o prekidu vatre koji je okončao Prvi svetski rat, Nemačka je pobednicima morala da plati ogroman novac. Nemačkoj vladi je bio preko potreban novac, pa su prodale obveznice (dug) Rajhsbanci, nemačkoj centralnoj banci.
Ovaj postupak doveo je do toga da je vlada štampala toliko maraka (tadašnja nemačka valuta) da je tempo inflacije u Nemačkoj ubrzan u hiperinflaciju početkom 1920-ih. Cena vekne hleba za samo 4 godine popela se sa 1,2 marke na 428 biliona maraka.
Tokom i posle Prvog svetskog rata, SAD, Britanija, Francuska i mnoge druge vlade pratile su Nemačku u štampanju valute potpomognute državnim dugom.
To je dovelo do toga da su građani želeli da svoju papirnu valutu zamene za zlato, baš kao i penzioner iz priče o Kejnslandu.
Međutim, mnoge vlade su suspendovale konvertibilnost svojih valuta u zlato. Ovim potezom vlade su primorale svoje građane da drže nacionalnu papirnu valutu i gledaju kako se njihova ušteda smanjuje u vrednosti.
Da bi mogle da nastave da štampaju novac i da bi ga trošile na nepopularne programe za koje nisu mogle da skupljaju poreze za finansiranje – poput ratova.
Bretton Woods: Novi monetarni sistem
Nakon razaranja koja su donela dva svetska rata, vlade su uspostavile novi globalni monetarni sistem prema Bretton Woods-ovom sporazumu iz 1944. godine.
Prema ovom sporazumu, valuta svake države konvertovala se po fiksnom kursu sa američkim dolarom. Američki dolar je zauzvrat predstavljao zlato po stopi od 35 USD za jednu trojsku uncu zlata*.
Sve globalne valute su stoga još uvek bile jednostavna reprezentacija zlata, putem američkih dolara kao posrednika. Redovni građani više nisu mogli da otkupljuju svoje valute za zlato iz Sjedinjenih Država. Međutim, strane centralne banke mogle bi da dođu u Sjedinjene Države da bi zamenile dolare za zlato po stopi od 35 USD za jednu uncu zlata.
Međutim, vlada Sjedinjenih Država nije uvek držala dovoljno zlata da podrži sve dolare u opticaju. Američka vlada nastavila je da finansira proširene socijalne i vojne programe prodajom državnog duga svojoj centralnoj banci, Federalnim rezervama, koja je povećala ponudu dolara bez povećanja ponude zlata koja podupire te dolare.
*Trojna unca je standardna mera čistog zlata i ima malo veću težinu od normalne unce.
Propast Bretton Woods-a
Tokom 1970-ih, sve veći troškovi rata u Vijetnamu i stranih vlada koje su otkupljivale svoje dolare za zlato, stvorili su pritisak na Trezor Sjedinjenih Država.
Ponuda dolara je porasla, dok je zlato u posedu Sjedinjenih Država opalo. Od 1950. pa do početka 1970-ih, rezerve zlata koje je držala vlada Sjedinjenih Država smanjile su se za više od 50%, sa 20 metričkih tona na samo 8 metričkih tona.
Godine 1970. država je imala zlata u vrednosti od samo 12 biliona dolara po zvaničnom kursu od 35 dolara za trojsku uncu zlata. Tokom ovog istog vremenskog perioda, ukupna ponuda američkih dolara otišla je sa oko 32 biliona USD na skoro 70 biliona USD.

Zvanične rezerve zlata u SAD-u su naglo padale od 1950. do 1970. godine, dok su se dolari u opticaju povećavali. Izvor: Wikipedia, DollarDaze.org
Američka vlada nije bila u stanju da potkrepi dolare zlatom od 35 dolara po trojnoj unci, što dovelo do rizika za čitav globalni monetarni sistem.
Početkom sedamdesetih godina, trojna unca zlata trebala je da vredi 200 USD da bi u potpunosti podržala sve američke dolare u opticaju. Rečeno na drugi način, Sjedinjene Države su pokušavale da kažu svetu da jedan dolar vredi 1/35 trojne unce zlata, ali u stvarnosti dolar je vredeo samo 1/200 trojne unce.
Kad su strane vlade trebale da pribave dolare za međunarodnu trgovinu i rezerve, bile su opelješene. Francuska vlada je to shvatila šezdesetih godina prošlog veka i počela je da prodaje svoje američke dolare za zlato po zvaničnom kursu od 35 dolara za trojsku uncu zlata.
Zemlje su počinjale da se bude iz šeme američke vlade. SAD su krale bogatstvo putem emisione dobiti, prodajući dolare za 1/35 trojne unce zlata, kada su vredeli samo 1/200 trojske unce.
Nixonov Šok ulazi u ’tradicionalni’ novac
Da bi kuća od karata mogla da ostane na mestu, predsednik Nixon je 1971. najavio da će američka vlada privremeno da obustavi konvertibilnost dolara u zlato.
Strane vlade više nisu mogle da polažu pravo na zlato svojim papirnim dolarima, a dolar više nije bio “poduprt” zlatom. Nixon je tvrdio da će ovo stabilizovati dolar.
50 godina kasnije, kristalno je jasno da je ovo samo pomoglo dolaru da izgubi vrednost i da ovaj “privremeni” program još uvek traje.
Pre 1971. godine, sve globalne valute bile su vezane za američki dolar putem Bretton Woods-ovog sporazuma. Kada je Nixon promenio američki dolar iz dolara podržanog u zlatu u dolar podržan dugom, ovim je promenio i svaku drugu valutu na Zemlji.
Sam je učinio da se celokupna svetska ekonomija zasniva na dugovima. Valute više nisu predstavljale zlato, već su predstavljale vrednost državnog duga.
Zlatni Standard se nikada nije vratio
Konvertibilnost američkih dolara u zlato – zlatni standard – nikada se nije vratio.
Od 1971. godine, čitav globalni monetarni sistem pokreće se tradicionalnim “fiat” valutama: poverenjem u vladine institucije da održavaju valutni sistem.
Većina valuta podržana je kombinacijom duga njihove vlade i drugih tradicionalnih valuta poput dolara i evra. Papirne valute više nisu podržane zlatom, imovinom koja je više od 5000 godina služila kao težak novac.
Danas vas vlade prisiljavaju da plaćate porez u njihovoj valuti i manipulišu saznanjima oko novca kako bi osigurale da potražnja za njihovom valutom ostane velika.
To im omogućava da neprestano štampaju više valuta, da bi je potrošili na vladine projekte, uzrokujući inflaciju cena koja jede i smanjuje bogatstvo i plate.
Američka vlada sada prodaje državne obveznice (dugove), poznate kao obveznice Trezora SAD, eng. US Treasuries, komercijalnim bankama u zamenu za američke dolare.
Vlada koristi te dolare za finansiranje svog budžetskog deficita. Komercijalne banke prodaju mnoge obveznice Trezora SAD, koje su kupile, američkoj centralnoj banci, Federalnim Rezervama.
Federalne rezerve plaćaju komercijalnim bankama sveže štampanim novcem “pomoću računara i upisivanjem količine na račun”, kako je rekao bivši predsednik Fed-a Ben Bernanke.
Ove komercijalne banke često zarađuju samo kupujući obveznice Trezora SAD od države i prodajući ih centralnoj banci. Kupujte nisko, prodajte visoko.
Centralne banke ovaj proces kupovine državnog duga – odnosno pozajmljivanja novca državi – nazivaju operacijama otvorenog tržišta.
Kada centralna banka odjednom kupi velike iznose duga, oni to nazivaju kvantitativnim ublažavanjem. Centralne banke javno najavljuju kupovinu državnog duga, ali vrlo malo ljudi razume šta to zapravo znači.
Euro, jen i svaka druga valuta koja se danas koristi funkcionišu slično kao američki dolar.
Da li će SAD ikada vratiti svoj nacionalni dug? Neobična stvar u vezi sa državnim dugom SAD-a je ta što vlada poseduje štampariju potrebnu za njegovu otplatu.
Kao rezultat toga, kada vlada duguje novac, oni samo pozajme još više novca da bi otplatile taj dug, povećavajući nacionalni dug.
Ako vam ovo zvuči kao Ponzijeva piramidalna šema, to je zato što ona to i jeste – najveća Ponzijeva šema u istoriji. Kao i svaka Ponzijeva šema, nastaviće se sve dok su ljudi koji kupuju Ponzijevu šemu budu uvereni da će im biti plaćeno nazad.
Ako ljudi i nacije prestanu da se zadužuju i koriste američke dolare jer nemaju poverenja u američku vladu ili vide da cena robe raste (tj. dolar postaje sve manje vredan), potražnja za dolarom će opadati, što će izazvati začaranu spiralu.
Ova spirala često završi u hiperinflaciji, kao što smo videli u novijoj istoriji sa Jugoslavijom, Venecuelom, Argentinom, Zimbabveom i mnogim drugim državama.
Ovo je način kako funkcioniše novac na vašem bankovnom računu. Novac svake nacije na svetu pati od istih problema kao i perle i novčanice u pričama o Njutoniji i Kejnslandu.
Kako banke i vlade kradu tvoj novac?
Tokom vekova, stigli smo do monetarnog sistema u kojem banke i vlade mogu da štampaju novu valutu za finansiranje svojih operacija i svojih prijatelja u zločinu, dok kradu bogatstvo svojih građana.
Šta će se desiti sa svetom kada novac bude mogao da štampa svaki narod na planeti?
- Bogatstvo onih koji su blizu pravljenja nove valute se povećava
- Vlada i politički povlašćena klasa ljudi, imaju pristup novoštampanom novcu pre svih ostalih, pa mogu da ga potroše pre nego što cene porastu. Na ovaj efekat pokazao je ekonomista Richard Cantillon sredinom 1700-ih i poznat je kao Cantillonov Efekat.
- Cena robe raste (poznato kao inflacija
- Ne raste sve roba istovremeno u ceni. Roba blizu mesta gde se proizvodi nova valuta – finansijski sektor i vlada – prva raste, i odatle uzrokuje efekt talasa na cene.
- Inflacija se često predstavlja kao promena cene potrošačke korpe, poznata kao Indeks Potrošačkih Cena, eng. Consumer Price Index (CPI). Vlada ima alate za manipulisanje ovim brojem kako bi osigurala da se ona čini niskom i stabilnom, kao što je objašnjeno u našem članku o inflaciji.
- Finansijska imovina često primećuje ogromnu inflaciju, ali bankari to ne nazivaju inflacijom – oni kažu da naša ekonomija cveta! Nakon što su američke Federalne rezerve učetvorostručile ponudu američkih dolara u šest godina nakon finansijske krize 2008. godine, banke koje su dobile te nove dolare, kupile su akcije i obveznice, stvarajući ogroman balon u cenama ove imovine.
- Štednja i životni standard stanovništva se smanjuju
- Plate su jedna od poslednjih “cena” u ekonomiji koja se prilagođava, jer se često povećavaju samo jednom godišnje. U međuvremenu, cene dnevnih potrepština te osobe koja zaradjuje platu neprestano rastu kako novi novac kruži ekonomijom.
- Najviše su pogođeni oni koji žive od plate do plate – a to je 70% Amerikanaca.
- Razlike u prihodima između bogatih i siromašnih se povećavaju, kao što se vidi na grafikonu ispod.

*Koncentracija dohotka na vrhu naglo je porasla od 1970-ih
Zašto i dalje imamo isti monetarni sistem?
Ako ovaj sistem bogate još više obogaćuje, a siromašne još više osiromašuje, dovodeći do političke nestabilnosti, zašto ga onda ne bismo promenili?
Najveći razlog zašto se ništa ne menja je verovatno to što puno toga ne znamo o samom sistemu. Svi svakodnevno koristimo valute svojih vlada, ali većina nas ne razume kako sistem funkcioniše i šta on čini našim društvima.
Obrazovni sistem, mediji i finansijski stručnjaci neprestano nam govore da je monetarni sistem previše komplikovan da bi ga normalni ljudi razumeli. Mnogi od nas se zato i ne trude da pokušaju.
Još nekoliko razloga zašto ovaj sistem nastavlja da opstaje:
- Mnogo je ljudi koji imaju direktnu korist od štampanja novog novca.
- Ti ljudi ne žele nikakve promene i bore se da zadrže tu moć.
- Nacionalne valute su često pogodne
- Kreditne kartice, online bankarstvo i još mnogo toga čine upravljanje nacionalnim valutama i njihovo trošenje lakim i jednostavnim.
- Građani moraju da plaćaju porez u svojoj nacionalnoj valuti
- To stvara potražnju za tom valutom od svih građana, povećavajući njenu vrednost.
- Glavna međunarodna tržišta, poput nafte, denominirana su u dolarima.
- Nafta je potrebna svakoj zemlji na planeti, ali pošto mnogi ne mogu da je proizvode, moraju da je kupuju na međunarodnim berzama. Od 1970-ih na ovim berzama gotovo sva nafta se prodaje za dolare, što stvara potražnju za dolarima. Da bi se odmaknule od ovog sistema, zemlje bi trebale da pronađu novu valutu ili robu za trgovinu naftom, što zahteva vreme i rizike.
- Nije postojala dobra alternativa
- Uz globalnu ekonomiju u realnom vremenu, naš sistem digitalnog bankarstva koji koristi nacionalne valute je pogodan. Transakcija u tvrdom novcu poput zlata bila bi previše nezgrapna za današnji svet. Digitalna valuta pod nazivom Bitcoin, predstavljena 2009. godine, je rastuća alternativa koja nudi čvrst novac koji se kreće brzinom interneta.
Šta je novac, i zašto trebate da brinete?
Novac je alat koji olakšava razmenu dobara. Kao i svako drugo dobro, novac se pridržava zakona ponude i potražnje – povećanje potražnje povećaće njegovu vrednost, a povećanje ponude smanjiće njegovu vrednost.
Na ovaj način novac se ne razlikuje od kuće ili piletine. Međutim, velika prodajnost novca znači da je potražnja za njim uvek velika. Kao rezultat, novac mora biti težak za proizvodnju (a samim tim i ograničen u ponudi) ili će ga onaj ko ga može napraviti, stvoriti toliko, da vremenom više neće služiti kao zaliha vrednosti. Uskoro će izgubiti svoje funkcije kao sredstvo razmene i obračunske jedinice.
Najbolji novac u datoj ekonomiji je onaj koji se najslobodnije kreće – svi ga žele, lako je obaviti transakcije sa njim i koji sa vremenom dobro drži svoju vrednost. Nijedan novac nije savršen u svemu ovome, a neki ističu jednu funkciju novca na štetu drugih.
Iako se istorija ne ponavlja, ona se rimuje, a usponi i padovi monetarnih sistema imaju jasne ritmove. Uspon i pad monetarnog sistema često sledi opšti obrazac koji smo videli u pričama o agri perlama i Kejnslandu: pojavljuje se odredjenji oblik novca koji pomaže ljudima da efikasnije trguju i štede, ali na kraju gubi na vrednosti kada neko shvati kako da ga jeftino stvori u velikoj količini. Međutim, tokom dugog perioda vremena, monetarni sistemi su se poboljšali u sve tri funkcije novca.
Na primer, zlato je tokom vremena dobro služilo kao zaliha vrednosti. Međutim, naša međusobno povezana ekonomija ne bi mogla efikasno da funkcioniše ako bi trebalo da fizičko zlato zamenimo robom i uslugama. Mnogo je lakše kretati se na papirnom i digitalnom novcu, ali istorija nam govori da su vlade i bankari iskoristili ove oblike novca za krađu bogatstva putem inflacije.
Današnji globalni monetarni sistem je vrlo zgodan, a digitalna plaćanja i kreditne kartice olakšavaju trošenje novca. Ovo skriva stalnu inflaciju koja nagriza vrednost svake jedinice novca i dovodi do sve većeg jaza u bogatstvu.
Nadam se da je ovaj članak proširio vaše razumevanje novca i njegove uloge u društvu. Ovo je samo početak svega što treba istražiti o novcu: za kasnije su sačuvane teme o inflaciji, kamatnim stopama, pozajmljivanju, poslovnim ciklusima i još mnogo toga.
Efikasnija Ušteda Novca
Možda se pitate kako zaštititi svoju štednju kada svaki oblik često korišćenog novca i investicija pati od inflacije ponude – koja umanjuje vrednost i prenosi bogatstvo onima koji mogu da stvore novac ili investiciju. Možda se čini da se ništa na planeti danas ne može kvalifikovati kao ‘težak’ novac, ali dve stvari ipak ostaju: zlato i njegov noviji rođak Bitcoin. Obe ove stvari je neverovatno teško proizvesti, a jedna od njih se kreće brzinom interneta i može se čuvati u vašem mozgu.
Ako želite da saznate više o Bitcoin-u kao sredstvu za zaštitu vaše ušteđevine, pročitajte ovde. Ako ste već spremni za kupovinu Bitcoin-a, pogledajte moj vodič za kupovinu Bitcoin-a. Možete početi sa investiranjem sa samo 5 ili 10 €.

Zasluge
Hvala svima koji su pomogli u izradi i uređivanju ove serije o novcu: @ck_SNARKS, @CryptoRothbard, Neil Woodfine, Emil Sandstedt, Taylor Pearson, Parker Lewis, Jason Choi, mojoj porodici i mnogim drugima.
Hvala svima koji su ovo inspirisali i razvili ključne ideje koje su ovde primenjene: Friedrich Hayek, Carl Menger, Ludwig Von Mises, Murray Rothbard, Saifedean Ammous, Dan Held, Pierre Rochard, Stephan Livera, Michael Goldstein, i mnogi drugi.
Molim vas da šerujete! Ako vam je ovaj članak otvorio oči o tome kako funkcioniše naš novac i finansijski sistem, kontaktirajte me ili ostavite komentar!
Ako vam se sviđa moj rad, molim vas da ga podelite sa svojim prijateljima i porodicom. Cilj mi je da svima pružim pogled u ekonomiju i na to kako ona utiče na njihov život.
-
 @ daa41bed:88f54153
2025-02-09 16:50:04
@ daa41bed:88f54153
2025-02-09 16:50:04There has been a good bit of discussion on Nostr over the past few days about the merits of zaps as a method of engaging with notes, so after writing a rather lengthy article on the pros of a strategic Bitcoin reserve, I wanted to take some time to chime in on the much more fun topic of digital engagement.
Let's begin by defining a couple of things:
Nostr is a decentralized, censorship-resistance protocol whose current biggest use case is social media (think Twitter/X). Instead of relying on company servers, it relies on relays that anyone can spin up and own their own content. Its use cases are much bigger, though, and this article is hosted on my own relay, using my own Nostr relay as an example.
Zap is a tip or donation denominated in sats (small units of Bitcoin) sent from one user to another. This is generally done directly over the Lightning Network but is increasingly using Cashu tokens. For the sake of this discussion, how you transmit/receive zaps will be irrelevant, so don't worry if you don't know what Lightning or Cashu are.
If we look at how users engage with posts and follows/followers on platforms like Twitter, Facebook, etc., it becomes evident that traditional social media thrives on engagement farming. The more outrageous a post, the more likely it will get a reaction. We see a version of this on more visual social platforms like YouTube and TikTok that use carefully crafted thumbnail images to grab the user's attention to click the video. If you'd like to dive deep into the psychology and science behind social media engagement, let me know, and I'd be happy to follow up with another article.
In this user engagement model, a user is given the option to comment or like the original post, or share it among their followers to increase its signal. They receive no value from engaging with the content aside from the dopamine hit of the original experience or having their comment liked back by whatever influencer they provide value to. Ad revenue flows to the content creator. Clout flows to the content creator. Sales revenue from merch and content placement flows to the content creator. We call this a linear economy -- the idea that resources get created, used up, then thrown away. Users create content and farm as much engagement as possible, then the content is forgotten within a few hours as they move on to the next piece of content to be farmed.
What if there were a simple way to give value back to those who engage with your content? By implementing some value-for-value model -- a circular economy. Enter zaps.

Unlike traditional social media platforms, Nostr does not actively use algorithms to determine what content is popular, nor does it push content created for active user engagement to the top of a user's timeline. Yes, there are "trending" and "most zapped" timelines that users can choose to use as their default, but these use relatively straightforward engagement metrics to rank posts for these timelines.
That is not to say that we may not see clients actively seeking to refine timeline algorithms for specific metrics. Still, the beauty of having an open protocol with media that is controlled solely by its users is that users who begin to see their timeline gamed towards specific algorithms can choose to move to another client, and for those who are more tech-savvy, they can opt to run their own relays or create their own clients with personalized algorithms and web of trust scoring systems.
Zaps enable the means to create a new type of social media economy in which creators can earn for creating content and users can earn by actively engaging with it. Like and reposting content is relatively frictionless and costs nothing but a simple button tap. Zaps provide active engagement because they signal to your followers and those of the content creator that this post has genuine value, quite literally in the form of money—sats.

I have seen some comments on Nostr claiming that removing likes and reactions is for wealthy people who can afford to send zaps and that the majority of people in the US and around the world do not have the time or money to zap because they have better things to spend their money like feeding their families and paying their bills. While at face value, these may seem like valid arguments, they, unfortunately, represent the brainwashed, defeatist attitude that our current economic (and, by extension, social media) systems aim to instill in all of us to continue extracting value from our lives.
Imagine now, if those people dedicating their own time (time = money) to mine pity points on social media would instead spend that time with genuine value creation by posting content that is meaningful to cultural discussions. Imagine if, instead of complaining that their posts get no zaps and going on a tirade about how much of a victim they are, they would empower themselves to take control of their content and give value back to the world; where would that leave us? How much value could be created on a nascent platform such as Nostr, and how quickly could it overtake other platforms?
Other users argue about user experience and that additional friction (i.e., zaps) leads to lower engagement, as proven by decades of studies on user interaction. While the added friction may turn some users away, does that necessarily provide less value? I argue quite the opposite. You haven't made a few sats from zaps with your content? Can't afford to send some sats to a wallet for zapping? How about using the most excellent available resource and spending 10 seconds of your time to leave a comment? Likes and reactions are valueless transactions. Social media's real value derives from providing monetary compensation and actively engaging in a conversation with posts you find interesting or thought-provoking. Remember when humans thrived on conversation and discussion for entertainment instead of simply being an onlooker of someone else's life?
If you've made it this far, my only request is this: try only zapping and commenting as a method of engagement for two weeks. Sure, you may end up liking a post here and there, but be more mindful of how you interact with the world and break yourself from blind instinct. You'll thank me later.

-
 @ bc6ccd13:f53098e4
2025-05-24 15:55:20
@ bc6ccd13:f53098e4
2025-05-24 15:55:20It wasn’t so long ago that the mainstream conversation around population was exclusively focused on the dangers of overpopulation. The fatal flaws in the Malthusian theory had yet to be disproven clearly and obviously by observable demographic trends. That’s been gradually changing, and while it’s hardly a mainstream consensus, concerns about falling birthrates and the risk of population collapse have taken over the population conversion on the political right, and sometimes beyond.
There’s no questioning the data at this point. Fertility rates over most of the world have been in precipitous decline, and if the current trajectory continues, global population will peak very soon and fall rather dramatically. And even the falling population itself is much less of a threat than the aging population that will inevitably precede it. Having a large cohort of older and retired people and a small cohort of young workers is an existential threat to the modern welfare state, and to the entire credit-based fiat monetary system that supports it. But that’s a subject for another day.
There are a multitude of different theories that attempt to explain why this is happening. I’ll name some of the most common ones:
-
Increased education and employment opportunities for women
-
Urbanization
-
Economic factors
-
Access to contraception
-
Changing social and cultural norms
-
Delayed marriage
-
Improvements in infant mortality rates
-
Government policies
-
Environmental concerns
-
Pornography
-
Feminism
-
Endocrine disrupting chemicals
-
Dating apps
Most rational thinkers agree there must be multiple factors playing a role. But the fact that the problem is so wide-spread, and populations that seem to be resisting the trend are so rare, shows that the strongest underlying factors are cross-culturally powerful and not easily resisted or reversed with marginal cultural differences and standard public policy efforts.
While populations that resist the trend are rare, they are not quite non-existent. A few groups stand out for their persistently high fertility rates. On a geographic basis, sub-Saharan Africa is the only major region still maintaining above-replacement fertility rates. For various reasons, I don’t think Africa is the most useful place to look for answers on what’s causing the decline elsewhere or how it could be reversed. One reason is that Africa seems to be following the global pattern, just with a lag. In another few decades the data may look very different, just like it does for South America today compared to 20 years ago.
In my opinion, a more useful place to look for data is in smaller population sub-groups within a geographic area that have fertility rates significantly higher than the general population levels. Rural populations in general have higher fertility rates than urban populations, but the difference isn’t really enough to consider it significant. The groups that fit this category well seem to be exclusively religious. These include certain Christian denominations in the traditional Anabaptist category including the Amish, Mennonites, and Hutterites, Muslims in some areas, and Jews, particularly the most orthodox sects. Mormons recently fell out of the high-fertility religious group category, which would also make for some interesting research.
It would be fascinating to compare these groups and see what they have in common outside just being religious in nature. I don’t have the knowledge to make that comparison. Instead, I’m going to focus on the group that’s often referenced and analyzed by people without much personal knowledge, the Amish.
I have read numerous articles and comments that reference the Amish to support this or that theory on the cause of falling fertility. One thing I notice is an obvious lack of understanding of the Amish culture, which leads to faulty arguments that don’t reflect reality. This isn’t surprising, given the insular and poorly-understood nature of the culture, the plethora of ridiculously incorrect “Amish” reality TV shows and pop culture myths, and the fact that the number of people with firsthand knowledge of Amish culture from an insider perspective who also write about demographic trends on any public platform is probably zero.
Well, was zero. I’m about to make that one.
My Qualifications
Since I’m claiming to have this knowledge, it’s only fair to give a little background as to how I got it. I choose to stay anonymous on the internet, and given that this is personal information that could make it significantly easier to dox me, I’ll be deliberately vague.
My parents were both born in Amish families. They didn’t stay, opting to leave the Amish church and culture before getting married and starting their family. My grandparents were all Amish, and all my cousins and most of my extended family remain Amish to this day. My parents didn’t move out of the Amish community, staying in the area and joining a conservative Mennonite church that was about the closest thing to being Amish without actually being Amish. The Mennonite community has a generally good relationship with and a lot of respect for the Amish community, given their deep similarities and shared history and cultural background.
I grew up interacting regularly with Amish relatives, neighbors and community members, speaking the Pennsylvania Dutch my parents taught us and used exclusively at home. I’m very certain that a real deep understanding of Amish culture is almost impossible without speaking their language, just like many other cultures around the world. The Amish speak English as their second language, but there are aspects of their culture that aren’t spoken about in English.
This lifelong proximity to and interaction with the Amish community has, I believe, given me some unique insights into the factors supporting their high fertility rates that no amount of academic research will ever uncover.
Who are the Amish?
First, some basics.
The Amish are a traditionalist Christian denomination. The way to understand the Amish is as a religious denomination first, and a culture second. Getting the two mixed up makes it impossible to understand why the Amish live the way they do.
Sure, their unique lifestyles makes them noteworthy as a group. But that lifestyle is based on and maintained by their religious beliefs and convictions.
Fundamentally, the Amish attempt to live out the Gospel as Jesus taught in the Sermon on the Mount. They believe their church has done so historically, and that the best way to make sure they keep doing so in the future is to view any changes to their traditional lifestyle with extreme skepticism and resistance.
The two primary doctrines that separate them from the mainstream Protestant Reformation, which is their group’s origin, are the doctrines of nonconformity and nonresistance. They apply the doctrine of nonconformity, the command to “be not conformed to this world: but be ye transformed by the renewing of your mind, that ye may prove what is that good, and acceptable, and perfect, will of God” in both a spiritual and a practical sense. They believe that Christians are to be radically different from non-Christians, both in their beliefs and attitudes, and in their lifestyle and appearance. And they apply the command to “resist not evil”, nonresistance, to mean that it’s a sin to use physical force or violence against another person for any reason whatsoever. They don’t make any exception for military service of any type, which they object to as a matter of conscience, or for self-defense, which they refuse to engage in even if it means death for themselves or their family.
The Amish do not practice infant baptism. Their young people must choose to be baptized and formally become members of the church, usually in their late teens or early twenties. As part of the baptism ceremony, they make a vow to remain faithful to God and the church until death. The Amish, as a church, interpret this vow to mean that the new church member will remain a member of the Amish church for life. Leaving the Amish church after making this vow and being baptized is viewed as breaking the vow, and is the justification for their practice of shunning, or the ban. Those who do so are cut off from contact with the community in various ways. Typically they won’t eat a meal with a shunned person, ride in a car a shunned person is driving, or do business with a shunned person. That includes immediate family. Failure to enforce this shunning against someone, even your own child, can result in running afoul of the church leadership and also being excommunicated and shunned.
This punishment, however, only applies to people who leave the church after baptism. Those young people who choose not to be baptized and leave the church instead are free to be treated just like any other non-Amish person, although their family essentially disown them and treat them like a shunned person anyway, if they’re especially strict and upset about the betrayal of Amish values.
Most Amish people don’t believe that the Amish are the only true church, or that only Amish people are true Christians. Most are accepting of other conservative Anabaptist denominations, and respect their values and practices as a different but valid way to be Christian. Church teaching strongly suggests that those who fall under the ban are living in sin and won’t make it to heaven. Most individuals, though, probably wouldn’t agree with that in every case if they were free to give their true opinion on the issue.
The Amish maintain a fertility rate of around 6 to 7 children per woman. Some recent research suggests this may be starting to fall somewhat, but the data isn’t extensive enough to make a solid judgement yet.
There are a wide variety of different “flavors” of Amish in different areas of the US, a fact they’re very aware of. The data strongly indicates that the most conservative and technologically primitive communities have slightly higher fertility rates and significantly higher retention rates of young people.
Why do the Amish Maintain High Fertility Rates?
Okay, enough background. Time to dive into the reasons I believe the Amish maintain their historically high fertility rate despite living in a developed, modern economy surrounded by people with dramatically sub-replacement fertility rates.
I thought long and hard about the best way to approach this. Going through a list of factors topically seemed like the obvious one. But the more I thought it through, the less I liked it. For one, how do you arrange the factors? Order of importance? How do you decide that? Also, the factors are so inter-related that they’ll be very tough to separate and understand individually. Finally, it seems dry and boring. Nobody needs that.
So I’m going to try something different. I’m going to approach it from a narrative angle. I’ll try to describe the life of a typical Amish person, from birth to death, in a chronological way. That’s the best approach to present it in a way that makes the culture relatable, while also tying the different factors together logically.
I’ll describe the experience for both men and women as best I can, and try to present the various factors encouraging high fertility as I see them at the appropriate part of the story.
This will likely be an article that gets revised later to address any questions that come up, so don’t consider it the final word on the subject.
Alright, time to get started.
Subscribed
First off, this might seem obvious, but the typical Amish baby is born into a large family. On average, they’ll have 5 or 6 siblings, and more is not at all uncommon. Families of 10 won’t raise an eyebrow, and 12-16 children aren’t unheard of, especially in the past when mortality was higher and second marriages were more common among younger widowers who went on to have children with their second wife. Humans are social creatures, and the environment and people we grow up surrounded by have a strong influence on our frame of reference. Studies have shown that women are very unlikely to have more children than their mother had. The number of siblings in your family, and in families you observe and interact with, doesn’t determine the number of children you will have, but it does strongly influence the number of children you feel is a “normal” amount. That makes it a kind of ratchet effect, where it’s very unlikely that a generation raised in homes with one or two children will go on to have larger families of their own collectively.
This cultural norm of large families establishes a kind of inertia that normalizes high fertility right from birth. Amish children grow up surrounded by siblings, observing, and as they get older, helping with the care and maintenance of a large family. All their relatives, cousins and extended family are also likely to belong to large families. The average Amish child grows up with dozens of first cousins, and sometimes hundreds of more distant cousins, many of whom they likely know well and socialize with regularly. This experience establishes a mental framework where a large family is assumed to be the default. And there is no stronger human tendency than the urge to fit in with the people around you.
Amish children grow up with strong gender norms taught from a very young age. The Amish culture follows strict and conservative gender roles. Boys and men do male things, girls and women do female things, and there is little effort or desire to create any overlapping space.
Boys grow up doing traditionally masculine things. They play outside, do chores on the farm, help their dad with his work, probably get a BB gun before age 10, go hunting and fishing, play sports, and generally prepare for a lifetime of physical labor and providing for a wife and family.
Girls grow up doing traditionally feminine things. They help care for younger siblings, help with housework, play with dolls, learn to cook and preserve food, learn to sew, and generally prepare for a lifetime of caring for and raising children and maintaining a large household.
It’s a common misconception that the Amish are mostly farmers who live off the land, subsistence style. That’s not at all accurate. While there are still Amish who make their living farming, at least in some areas, that has become the exception. The large scale of modern agriculture means it takes a lot of acres and a lot of machinery to run a profitable commercial farming operation. The Amish reject the use of most modern agricultural machinery, which makes them uncompetitive in commercial agriculture outside more niche markets like dairy, produce, or greenhouses. And the fact that they live in small geographic communities with large families means they quickly buy up all available farmland in an area until they price themselves out of the market. Prime farmland in heavy Amish farming communities like Lancaster, Pennsylvania routinely sells for over $25,000 per acre, which is more than a commercial crop farming operation might bring in over a lifetime.
So the Amish have moved away from a primarily agriculture based economy to various other occupations. In some areas they work in RV factories. Most work in trades, primarily construction. Many are masons, carpenters, cabinet builders, mechanics, welders, etc.
But they reject the ownership of cars, so they still use their characteristic horses and buggies for transportation. In reality, they use cars for most of their transportation needs. But they don’t own cars or have driver’s licenses, so they rely on “Amish taxi drivers” to chauffer them around. The men hire a driver to take them to and from work, if they work in construction or some other job outside the home. The women hire a driver take them to town for their shopping or for other errands. The exception is church. They’re still required to drive to church in a horse and buggy, so every family must keep a horse for that reason, as a bare minimum. In many cases that’s the only time they ever use a horse and buggy, and if it weren’t for that requirement they wouldn’t own one at all.
But that requirement means every Amish family must own enough land to keep a horse, which takes a few acres and a small barn at minimum. This forces them to live in rural areas and raise their families in a somewhat agricultural environment, even if their occupation wouldn’t require that at all. So there are always chores for the children, animals to care for, and space to play outside with their siblings.
Amish children grow up with very limited exposure to mainstream cultural pressures. Their mothers inevitably raise them at home until they start school. They don’t have TV or cell phones, so they aren’t exposed to any mainstream culture on a daily basis.
The Amish have their own schools, typically small one room schools within walking distance of all the families who attend. The teachers are often young single people, always Amish. They primarily teach basic academics: reading, writing, arithmetic, geography, history, etc. While the Amish speak both English and Pennsylvania Dutch, many Amish children are first exposed to English on a daily basis when they start school. School is taught in English, although there is limited teaching of the High German the Amish use in their church services.
Amish children attend school until 8th grade. The schools run the minimum number of days required by the state, usually 160. There is no higher education beyond grade 8. No Amish attend college.
Amish children are taught from little up that they are not like other people. The differences between their culture and mainstream culture are emphasized, and Amish culture is praised as the ideal, at a religious level. They're taught that the way to do what’s right is to do what the church asks, and those who don’t do what the church asks are in the wrong.
The Amish rate and describe everyone on a scale from “high” to “low”. A person who isn’t Amish, who isn’t a Christian, is a “high” person, or an “English” person. To go from being Amish to being “English” is the worst, most damning, failure imaginable. The Amish are “low” people. The more strict and traditional an Amish sect, the “lower” they are. Being “low” is seen as a virtue. Other conservative Christian denominations, particularly other Anabaptist groups, are also considered “low” people and generally viewed favorably, but they aren’t as “low” as the Amish.
Amish boys grow up expecting to start work full time at age 14, and to work at some type of trade or physical labor. There are no white-collar career tracks, essentially. Entrepreneurship is encouraged, and many young Amish men start their own construction crew or home business in their 20s or 30s after a few years of experience working for someone else. Often Amish boys start off working for and with their dad, in whatever trade or business he operates. But if they’re not interested in that particular occupation, they’re free to find another. Amish businesses and tradesmen are always willing to hire young Amish boys and train them in a craft. A good work ethic is considered a virtue, and Amish are known for their skilled craftsmanship and willingness to work harder than the competition. These traits are taught and encouraged from little on up.
Amish men as a whole do very well financially. For one, they start working and developing skills and work ethic a decade earlier than the typical college graduate. The trades pay well, and of course anyone could take advantage of that, but the mainstream narrative discourages men from pursuing a trade career by labeling it low status and keeping them in education until their prime years to gain a work ethic are past. It’s not uncommon for young Amish men just out of 8th grade to land a job on a carpentry crew for $25-30 an hour. With bonuses, some of them are bringing in $90k/year before age 20. Another advantage young Amish men have is lower expenses. They can certainly find places to spend their money, typically hobbies like hunting and fishing, but things like expensive designer clothes and accessories or overpriced car payments aren’t really an option. They also benefit from the Amish exemption to Social Security taxes. The Amish don’t pay into or collect Social Security. More on that later, but it helps immensely to keep more of your paycheck in your early prime working years.
Amish girls grow up expecting to get married at a young age and raise a large family as a traditional housewife. Amish girls aren’t encouraged to have a “career”, and the idea would be silly to them. They are expected to work, but the work is either helping their mom with the household, working on the family farm or business, or doing something like teaching school or working at an Amish farmer’s market to pass the time between leaving school and marriage. It’s never viewed as a permanent occupation, because marriage and motherhood is the default aspirational lifestyle. A common job for young Amish girls is working as a “maid” to help a new mother with housework at the end of pregnancy and for the first few months after childbirth. All new mothers can get this type of help if they want, and it will usually be a younger sister, cousin, or niece of appropriate age. Otherwise the community will find a suitable girl who’s available for the job. A “maid” will sometimes travel to a different Amish community for this reason, given how large extended families are and how frequently Amish families move across the country to a different community. This is often an opportunity for them to attract the attention of a young man outside their local community, and is one of the only ways for a long-distance relationship and marriage to begin.
Amish young people are expected to live with their parents until marriage, with very few exceptions. They’re also typically expected to work for their dad in the family business for no pay, and to give any earnings they make at a day job outside the home to their parents. This is typically expected until age 21, or until they get married, whichever comes first. More recently, with the rising cost of land and housing, it’s becoming more common to make age 18 the cutoff. And when a young couple is engaged, the parents typically allow them to start saving their income for their future household. This practice helps parents offset some of the expenses of raising such large families, along with the fact that no money is spent on higher education. It also provides one strong incentive to marry as early as possible.
Amish culture revolves around family and the community. Extended families are large, and people are expected to know and interact with their family. Conversation with a stranger at a social event invariably starts by asking their name, then asking who their parents, grandparents, and other relatives are until some distant family connection or a mutual acquaintance is found. Since the Amish community has a small pool of family names, and tends to heavily favor certain Biblical first names, enough people end up with the same name to make things really confusing. People are often identified by two or three generations of their family, for example “Sam Yoder’s John’s Amos” for an Amos Yoder who’s father was John Yoder and grandfather Sam Yoder.
Social activities are either family events or church events, or both. Weddings and funerals are the main social functions other than church services, and people are expected to attend as many as possible among their family and extended family, regardless of the distance. Given the large family sizes, most Amish have dozens of first cousins and many more distant cousins. Weddings and funerals can be almost weekly events. These are church events as well, so much of the local Amish community will usually attend. It will be an all day event, with the women and girls preparing a lunch and dinner for everyone. After the meal, the women and girls will wash the dishes and clean up, while the men sit around and talk. No cell phones, remember. Talking is the main form of social interaction. Topics typically include work, family news, hunting and fishing stories (Amish men hunt and fish with the same enthusiasm typical American men watch sports), horses, and interesting or funny stories about family and friends. Those with a knack for entertaining oratory are well respected and appreciated in the Amish community.
Of course the women do their fair share of talking as well, in the kitchen while cleaning up after the meal, and later in the living room where they join the men after the domestic work is done. The main topics of conversation always revolve around family, immediate and extended. News travels through the Amish community faster than any social media platform, because nothing builds Amish female status more than being the first to call with the news that great uncle so-and-so was injured in a farming accident or nephew so-and-so has a new baby, along with all the pertinent details about the name, size, and health of the baby and how the mother is doing and how many grandchildren that makes in total for the lucky grandparents.
While the adults are talking, the children are free to play either inside or preferably outside. Trampolines, climbing trees, playing in the hayloft, tag, volleyball, and softball are favorite activities at various ages. The younger boys and girls typically play together, but as they get older the girls spend more time visiting while the boys prefer more structured sports. Softball is a game for boys, but volleyball is popular with mixed teams of boys and girls at any age.
Visiting relatives or other community families is also a popular social activity, especially on “in-between Sunday”. The Amish have church every other week, and the week without church is often an opportunity to visit another family. Invitations are not expected or required, and anyone stopping by will be expected to stay for dinner and into the evening. At these type of events, the older children are often expected to sit and visit with the adults. Sitting still and being quiet are mandatory skills, since church services are 2 hours or longer and held in barns or sheds without air conditioning filled with backless wooden benches. Self-discipline is not an optional virtue, because the alternative is physical discipline.
As Amish young people enter their mid teen years, they go from childhood to youth. At a certain age, usually around 15 or 16, they officially become youth and enter the stage everyone is familiar with, “rumspringa”. That’s a Pennsylvania Dutch word that translates to “running around”. The Amish use it more as a verb, but pop culture has adopted it as a noun based on some wildly inaccurate reality TV shows and depictions.
The reality is, rumspringa varies widely from community to community, mostly based on what the parents and church leaders tolerate. Remember that Amish church membership is a fully voluntary decision, and Amish young people are free to join or not, as they decide. Late teens is the typical age for that decision. In the meantime, they are free to make their own decisions, subject to their parents’ rules. Breaking the rules can mean that at some point, they won’t be welcome to live in their parents’ household any more. That’s a fairly strong deterrent to the most extreme infractions.
At this stage, young Amish men will be buying their own horse and buggy, and both boys and girls will be permitted to attend the Sunday night “singing”. This is a social activity held at someone's house on Sunday evening, involving all the youth in the community coming together for dinner, playing volleyball, and singing German hymns together. The purpose is to provide a somewhat controlled social environment for young men and women to interact and hopefully meet their future spouse. Dating couples can attend together, and dates are permitted after the formal activities, with the young men often driving their date home late at night before finally heading home themselves.
Depending on the tolerance of the community, the informal activities can be a bit more permissive than singing hymns and playing volleyball. Often the buggies will become a typical teenage party scene, with alcohol, smoking, a radio, illicit smartphones and DVD players, and some less-than-reserved interaction between boys and girls. The punishment for getting caught can be severe, but in many cases the adults tend to turn a blind eye to what’s happening, and let the young people do as they please.
A lot more could be said about the dynamics of this cultural practice, but specifics vary so much between communities that I don’t think there’s much value in doing so. The point I think is relevant to this discussion is the question of sex.
There’s no reason to go off into the weeds on how much, if any, sex occurs. Premarital sex is absolutely forbidden. Does it happen anyway? Humans being human, certainly. How much? Probably very little in most cases. Getting pregnant, or getting someone pregnant, is the one transgression with inevitable life-changing consequences. The “shotgun wedding” is alive and well among the Amish, and getting a girl pregnant means marrying her or being expelled from the Amish community permanently, no exceptions. Besides that, getting pregnant outside of marriage is the most disgraceful and shameful thing a girl could do. It happens very very rarely, put it that way.
So casual sex within the community is basically off the table. What about casual sex with “English” people? This is where the Amish cultural practices play a big role. The Amish dress very distinctly. They can’t go anywhere in their traditional clothes without being instantly recognized. They also don’t drive cars, so going somewhere means getting a ride with someone. And their parents will usually keep an eye on their plans and whereabouts. So let’s imagine how an Amish teenager might go about finding a casual sexual encounter.
First off, getting ahold of a cell phone would be essential. They need some way to communicate with the outside world, and coordinate with their “partner in crime.” A lot of Amish teenagers do this, often with the help of slightly older people who have left the Amish, but keep ties with the community, maybe an older sibling or cousin. These are often the same people who buy alcohol for Amish teens.
Then, they need to get some non-Amish clothes. Remember, every trip away from home will take a willing driver, a plausible excuse in a community where everyone knows everyone, and the guarantee of being immediately recognized if seen in public. And the Amish parents know who the “bad kids” are, the ones who left but are willing to help their younger relatives and friends break the rules. Getting caught hanging around with them will probably mean a lot less trust and a lot less freedom in the future.
For the girls, a change of “English” clothes and a new hairstyle will let them blend in quite well. Of course, they can’t be caught leaving or coming home in those clothes, or have the clothes found at home. Lots of logistical hurdles everywhere. For the boys, they have a very distinctive haircut. A new change of clothes won’t fix that. There’s really no way for them to hide the fact that they’re Amish, even if the accent and the lack of a driver’s license don’t give them away.
Assuming they manage all that, and sneak away from home undetected, how will they find someone to hook up with? They’re very insulated from popular culture, and probably not at all comfortable in typical social situations. For the girls, there’s the added risk that an accidental pregnancy, or even just getting caught, would ruin their reputation and any chance of marriage and a family in the Amish community. So they’re unlikely to even try, unless they’re already fully intending to leave the Amish for good. That only really happens if they have a guy ready to marry them outside the Amish community, for reasons I’ll get into more later. Briefly, the Amish culture and schooling leaves women poorly prepared to support themselves outside that culture.
For the boys, there’s the typical difficulty men face in finding casual sexual partners. Multiply that by the difficulty of not having a car or driver’s license, not being experienced in mainstream social norms, plus that obvious and undisguisable Amish haircut. And all that ignores the lifelong teaching that casual sex is sinful and wrong, and those who engage in it are going against the teachings of God and the church. The entire culture is specifically designed to discourage casual sex as strongly as possible, and it does an excellent job at that.
Why does that matter? Well, humans are all very much the same, with the same desires and instincts. And sex is one of the strongest of those desires. The Amish are certainly no different.
So the Amish religious practice and culture offers a very simple choice. You can choose sex outside of marriage, which will be difficult or impossible, occasional at best, and if you get caught will mean expulsion from the community your life is rooted in, and even if you don’t get caught will mean you’re committing a mortal sin that will keep you out of heaven if you don’t repent and change. Or, you can get married and have all the sex you want, and be respected and rewarded for it.
That’s really all it takes to sell the idea of marriage to most men.
When a couple does decide to get engaged, of course with permission from the girl’s father, the wedding happens within a reasonably short time, in acknowledgement of the temptation young people face in that situation.
So let’s take a little closer look at the gender differences between the choice to stay single or to marry. It’s helpful to lay out the different life paths available, and how they play out over time.
There are very few Amish who remain single throughout their life, and almost all of them are women. So let’s look at it through a man’s perspective first. What kind of life can a single Amish man expect?
First off, a lifetime of celibacy. There’s hardly any need to go further, that’s a deal breaker for most men. If they choose to stay single for some reason, most will leave the Amish completely rather than accept those terms.
So maybe it’s more useful to look at incentives for early marriage, which is the norm. I’m a strong believer that incentives create outcomes, so I’ll be taking a hard look at incentives throughout this article.
Young people are expected to live with their parents until marriage, in most cases. Remember, no going off to college either. So from age 14 on, they’re stuck living with Mom and Dad, working full time, and not even keeping their own income. That gets old fast. Getting married, moving out, and starting a family looks better every day. Besides that, Amish women do a lot to improve the lives of their men. The Amish are well known for their delicious food. Well, that’s because the Amish women cook and bake. As a single guy, moving out of Mom’s house means not getting delicious home-cooked food every day. And they don’t have an iPhone to order DoorDash either, so it’s pizza delivery, hiring a driver to go to a restaurant, or whatever you can cook yourself. And Amish boys don’t grow up learning how to cook, that’s women’s work. Same with making clothes. Amish mothers and wives sew clothes for their families, since they’re forbidden to wear commercially available clothes in general. So a single guy is dependent on his mom for new clothes as well. Same with washing clothes. Most Amish have fairly modern clothes washing machines, although they don’t use dryers. But washing and folding clothes isn’t a job most boys grow up doing, so they’re pretty lost if they have to try it.
All in all, there aren’t a lot of upsides to staying single longer than absolutely necessary. There are plenty of benefits to marriage, though. For one, marriage is seen as a necessary step to full maturity as a man. It’s even expressed as a visible marker. Single young men typically stay clean-shaven. Once they get married, shaving is completely forbidden, and they are required to grow out a full beard. So the difference between married and single men is obvious at first glance, and is acknowledged as a marker of full maturity.
Then of course there’s the sexual access. No explanation needed.
Then there are all the benefits of an improved lifestyle a stay-at-home wife provides. That includes cooking, cleaning, washing clothes, caring for a garden, preserving food, helping with farm work or chores, and helping with his business. Many Amish wives are very involved in their husband’s career or business, whether that’s managing the bookkeeping, working in the greenhouses, or helping with daily chores on the farm. While most Amish communities use quite modern household appliances, powered with batteries, kerosene, or air pressure, the work of maintaining a household is still much more involved than for the typical American household. Especially when it comes to sewing, which very few American women do at all, but which took a large percentage of women’s time only a few generations ago. Among the Amish it still does.
I’m only focusing on the incentives for marriage right now, because that’s the first step. Of course, most married couples today don’t have 5-8 children, so there’s more to the story. But universal marriage, particularly early marriage, is an essential part of the puzzle.
Shifting focus to the women, here the picture is even more clear. Almost all lifelong single Amish people are women, and that’s not by choice. The Amish still maintain the “old maid” category that used to be part of mainstream culture. Single Amish women are almost invariably single because no man offered to marry them. Here’s why.
If single life is unappealing for Amish men, it’s positively bleak for women. Marriage and family life is the aspirational goal they’re taught from little up. And for good reason.
With their eighth-grade education, and without a driver’s license and car, their income earning potential is very limited. Most young women who aren’t busy on the farm or with the family business work as schoolteachers, housecleaners, babysitters, or cooks and servers at Amish restaurants or farmers’ markets. None of these jobs pay well. Enough to buy a few personal items, but not enough to buy a house or support even one person. And while it might be acceptable for a single Amish man to eventually buy a house and move out, at some point in his late 20s or early 30s, it’s really not acceptable at any age for an Amish old maid. Those old maids typically end up living with their parents, caring for them in old age, working the same type of jobs young girls do, and probably hoping that at some point an older widower with a family will show up and propose.
Marriage has massive lifestyle benefits for women, even more so than for men. Amish men typically do well financially, and often work in construction as well, or have friends and relatives who do. Amish houses are very nice and well constructed to say the least, and the wife gets the house she wants, the way she wants it. Being stingy with a house for your wife isn’t part of an Amish man’s mentality. Amish women are well rewarded for all their hard work keeping house, with a house they’ll be happy keeping. And of course a nice farm or at least some acreage, with space for a big garden, a barn for any animals, and space for greenhouses or whatever she needs for any home business ambitions she might have.
Along with that, Amish women have a lot of flexibility when it comes to spending money. Many Amish women handle most of the family finances. And the money her husband earns is family money, not his money. While the husband has final say in financial decisions, most Amish men don’t say no to their wives’ purchase requests often. Married Amish women have access to all the creature comforts the church allows to make their lives as pleasant as possible.
When it comes to status, the benefits are just as clear. Amish life revolves around family, and nothing is higher status than a thriving family of your own. The Amish version of posting exotic vacation pictures on Instagram is showing up to a social function with your new baby. It’s the automatic center of attention for weeks, until a newer baby show up in the community. And the default topic of conversation is always a woman’s children and their growth and development. Young girls grow up dreaming of the day they can join those conversations, and old maids are always outsiders in a certain sense, pitied by everyone else for their misfortune.
Being an old maid means being poor, low status, pitied by other women, and destined to live with your parents until they pass, with your only bitter-sweet consolation being the role of aunt to your dozens of nieces and nephews and maid to your sisters and sisters-in-law through their many pregnancies. Getting married means access to a man’s income, a nice new house just the way you want it, a farm, and an automatic status boost as a mother and eventually grandmother who always has lots to contribute to the conversation at social events.
As you can imagine, the incentives strongly favor marriage from both directions. Men benefit through improved lifestyle, status, and access to sex. Women benefit through improved lifestyle, economic opportunity, and status in the social hierarchy.
Given that the selection pool for potential partners is limited, mostly to the local Amish community, or occasionally another Amish community if there’s some interaction through family ties or social events, assortative mating is the norm. Young people can be choosy, sure. But they already know most of the people in their potential mating pool, and have probably known those people for most of their lives. They have a pretty good idea how desirable they are to potential partners, and the girls especially have to think long and hard about turning down a suitor. Men are always the initiators of a relationship, and the risk of turning down an eligible man and then never getting another offer, ending up as a dreaded old maid, is always lurking in the back of their minds.
Besides that, both men and women have multiple ways to improve their spouse’s life. Women are much more than just sexual objects. Their domestic role actually raises their husband’s standard of living significantly, in a way he can’t access as a single man. And men are all valuable to women, both for resources and for status as a wife and mother. Even a very average husband or wife is a massive lifestyle boost over remaining single.
By now it should be pretty clear why marriage is almost universal among the Amish, and marriage at what most would consider a young age (19-23) is more common than not. And I haven’t even mentioned any religious teaching, because frankly I don’t think that’s a major force on an individual level. The religious beliefs shape the social and material landscape, and that landscape provides the practical incentives that cause people to make the choices they do. The fact that an Amish interpretation of the Bible encourages marriage and children is one layer removed from the reasons individual 20-year-old Amish men and women choose to get married.
I pointed out earlier that getting married and having a high birthrate, or even getting married young and having a high birthrate, are not exactly the same thing. Plenty of married couples today have one, two, or even no children, even if they got married young enough to have ten if they chose to do so. So why are the Amish different?
There’s the too-obvious answer: they don’t allow the use of contraceptives. Occam’s razor and all, but it deserves a bit more explanation. After all, the Catholic Church doesn’t allow the use of contraceptives either, and look how well that’s working out for them. Of course the enforcement mechanism doesn’t have the teeth among Catholics that it has among the Amish, but that’s not the whole story. If they were motivated enough, there’d be a way to space the children out more, maybe end up without quite so many, without anyone knowing. That doesn’t happen, because the contraceptive ban is a dead letter when couples want to have as many children as possible, which the Amish typically do.
Again, I’ll go back to incentives. What are the incentives to have children specifically, as many as possible, and not just get married and “plan for a family one day”?
For one, status. For both men and women, a large family is a marker of high status. Parents are respected and honored for doing a good job of raising well-adjusted children.
Children are also less of a financial burden for the Amish. Their children are raised well, but not in a financially intensive way that’s become expected today. They don’t have to buy a new car or SUV to fit the family, they don’t buy every child a boatload of expensive electronic gadgets every birthday and Christmas, they don’t have to pay for frequent vacations or college tuition, and they don’t have to eat out or pay for takeout or pay for childcare or a house cleaner since the wife is handling all those domestic roles herself. And the Amish don’t practice helicopter parenting, so children are much more free to play and amuse themselves without constant supervision from their parents. They don’t have to be driven to 17 different weekly structured activities. They have a farm to play on and shelves full of books to read and some toys to play with if the weather is bad, and that’s about it. And of course as the family grows, the older siblings do a large percentage of the housework and help with the younger children.
The older teenagers that are working outside the home typically give their earnings to their parents, but this basically offsets the cost of raising them, so it isn’t really an incentive to have larger families, just the removal of a disincentive.
The strongest real incentive, other than increased status and cultural inertia, that I observe for large families is that the children are the parents’ retirement plan. The Amish don’t work at jobs that offer pensions or benefits. They are exempt from paying into, but also ineligible to receive, Social Security benefits. The Social Security exemption was granted on the basis that the Amish don’t need government payments to support them in old age, because the family and community will do that. And they do.
How does this work out in practice? First, the Amish don’t practice “retirement” the way most people think of it. They teach that work is honorable and every able-bodied man should work to support his family and to help those in need. So as long as a man is physically able to work, he’ll be employed and supporting himself and his wife. And Amish women move directly from the role of mother to the role of grandmother. It’s not at all uncommon, in fact, for a woman’s first grandchild to be born before her last child is born. So plenty of Amish children are an aunt or uncle at birth, and have a niece or nephew older than they are. Grandmothers are extremely involved in helping their daughters and daughters-in-law with childcare, so they don’t often have a big stretch of free time after their children grow up and move out. And besides that, there are still the significant household responsibilities to attend to.
As a couple gets older and perhaps less able to handle everything on their own, they often move to the home of one of their grown children. Typically not into the home directly, but into what’s called a “dody haus” (grandpa house) which might be a small detached house on the same property, or a separate wing of the larger house, like an in-law suite. Here they’re able to live independently, help care for the grandchildren next door, and still be nearby so their children and grandchildren can give any care they may need in old age. If the couple has an unmarried “old maid” daughter, she’ll typically still be living with them and will be the primary caregiver.
If someone doesn’t have children to care for them, the Amish community will find a way to care for them. Some more distant relative or maybe surviving siblings will step in to help. But the expectation and the rule is that your children and grandchildren will care for you after you’re no longer able to care for yourself. Finding yourself growing old without family is an unfortunate and unpleasant situation, regardless how much the community may try to fill that role. Just as throughout earlier stages of life, social functions and social status revolve around children and family, and anyone without them will be incomplete as a person, something of an inevitable outsider to the joys of life. The best insurance against a lonely and uncomfortable old age is a large family, among which there are certain to be sufficient resources to care for you. Many elderly Amish people die with well over a hundred grandchildren and great-grandchildren, and spend their later years constantly surrounded by children and young people who deeply appreciate and respect them. Being taught and shown that respect toward their own grandparents from a young age is a strong incentive to aspire to the same status one day.
I’m not sure exactly where this fits, but I should point out somewhere that the Amish have an absolutely zero tolerance policy toward divorce. There are no legitimate grounds for divorce whatsoever, and anyone who initiates a divorce will be excommunicated from the church and shunned. If an Amish person’s spouse initiates divorce proceedings, they won’t cooperate with those proceedings in any way. If the divorce happens through the legal system without their consent anyway, they can remain a church member in good standing only by staying celibate as long as their spouse remains alive. The only acceptable second marriage is in the case of the death of a spouse. In those cases, a quick remarriage is the rule among widows and widowers with young children, since raising a family is seen as a job for a married couple, not a single person.
It’s hard to say exactly how this stance against divorce influences marriage and fertility. But it certainly limits exposure to the idea of divorce as a “solution” to marriage difficulties, and incentivizes couples to work things out for their own life satisfaction. And it dramatically reduces the financial risks men face in the modern marriage system, where the potential to lose not only their family, but also a significant portion of their material wealth, raises strong disincentives to marriage. The physical realities of married life versus single life in a more low-tech environment probably discourage divorce, but the added threat of complete social and familial ostracization eliminate it almost entirely.
Conclusion
This article is my attempt to provide some insight into the Amish culture that might help us understand the factors causing their unusually high fertility rate. I’ve titled it as part one, because I plan to follow up with some of my personal opinions on how these insights relate to the broader society. I think a lot of the proposed causes of and solutions to the global demographic collapse are completely incorrect, and my opinion is based heavily on my observation of Amish culture. That will be the focus of part two of this article.
Feel free to comment and post questions. My biggest challenge in writing this article is the fact that I take my familiarity with Amish culture for granted to some degree, so I struggled to choose which points are relevant to understanding the culture for an outsider. I’m sure I skipped over plenty of important details that may leave readers feeling confused, so I’ll do my best to answer any questions you post, and update the article with pertinent information I missed.
-
-
 @ e3ba5e1a:5e433365
2025-02-05 17:47:16
@ e3ba5e1a:5e433365
2025-02-05 17:47:16I got into a friendly discussion on X regarding health insurance. The specific question was how to deal with health insurance companies (presumably unfairly) denying claims? My answer, as usual: get government out of it!
The US healthcare system is essentially the worst of both worlds:
- Unlike full single payer, individuals incur high costs
- Unlike a true free market, regulation causes increases in costs and decreases competition among insurers
I'm firmly on the side of moving towards the free market. (And I say that as someone living under a single payer system now.) Here's what I would do:
- Get rid of tax incentives that make health insurance tied to your employer, giving individuals back proper freedom of choice.
- Reduce regulations significantly.
-
In the short term, some people will still get rejected claims and other obnoxious behavior from insurance companies. We address that in two ways:
- Due to reduced regulations, new insurance companies will be able to enter the market offering more reliable coverage and better rates, and people will flock to them because they have the freedom to make their own choices.
- Sue the asses off of companies that reject claims unfairly. And ideally, as one of the few legitimate roles of government in all this, institute new laws that limit the ability of fine print to allow insurers to escape their responsibilities. (I'm hesitant that the latter will happen due to the incestuous relationship between Congress/regulators and insurers, but I can hope.)
Will this magically fix everything overnight like politicians normally promise? No. But it will allow the market to return to a healthy state. And I don't think it will take long (order of magnitude: 5-10 years) for it to come together, but that's just speculation.
And since there's a high correlation between those who believe government can fix problems by taking more control and demanding that only credentialed experts weigh in on a topic (both points I strongly disagree with BTW): I'm a trained actuary and worked in the insurance industry, and have directly seen how government regulation reduces competition, raises prices, and harms consumers.
And my final point: I don't think any prior art would be a good comparison for deregulation in the US, it's such a different market than any other country in the world for so many reasons that lessons wouldn't really translate. Nonetheless, I asked Grok for some empirical data on this, and at best the results of deregulation could be called "mixed," but likely more accurately "uncertain, confused, and subject to whatever interpretation anyone wants to apply."
https://x.com/i/grok/share/Zc8yOdrN8lS275hXJ92uwq98M
-
 @ 97c70a44:ad98e322
2025-03-05 18:09:05
@ 97c70a44:ad98e322
2025-03-05 18:09:05So you've decided to join nostr! Some wide-eyed fanatic has convinced you that the "sun shines every day on the birds and the bees and the cigarette trees" in a magical land of decentralized, censorship-resistant freedom of speech - and it's waiting just over the next hill.
But your experience has not been all you hoped. Before you've even had a chance to upload your AI-generated cyberpunk avatar or make up exploit codenames for your pseudonym's bio, you've been confronted with a new concept that has left you completely nonplussed.
It doesn't help that this new idea might be called by any number of strange names. You may have been asked to "paste your nsec", "generate a private key", "enter your seed words", "connect with a bunker", "sign in with extension", or even "generate entropy". Sorry about that.
All these terms are really referring to one concept under many different names: that of "cryptographic identity".
Now, you may have noticed that I just introduced yet another new term which explains exactly nothing. You're absolutely correct. And now I'm going to proceed to ignore your complaints and talk about something completely different. But bear with me, because the juice is worth the squeeze.
Identity
What is identity? There are many philosophical, political, or technical answers to this question, but for our purposes it's probably best to think of it this way:
Identity is the essence of a thing. Identity separates one thing from all others, and is itself indivisible.
This definition has three parts:
- Identity is "essential": a thing can change, but its identity cannot. I might re-paint my house, replace its components, sell it, or even burn it down, but its identity as something that can be referred to - "this house" - is durable, even outside the boundaries of its own physical existence.
- Identity is a unit: you can't break an identity into multiple parts. A thing might be composed of multiple parts, but that's only incidental to the identity of a thing, which is a concept, not a material thing.
- Identity is distinct: identity is what separates one thing from all others - the concept of an apple can't be mixed with that of an orange; the two ideas are distinct. In the same way, a single concrete apple is distinct in identity from another - even if the component parts of the apple decompose into compost used to grow more apples.
Identity is not a physical thing, but a metaphysical thing. Or, in simpler terms, identity is a "concept".
I (or someone more qualified) could at this point launch into a Scholastic tangent on what "is" is, but that is, fortunately, not necessary here. The kind of identities I want to focus on here are not our actual identities as people, but entirely fictional identities that we use to extend our agency into the digital world.
Think of it this way - your bank login does not represent you as a complete person. It only represents the access granted to you by the bank. This access is in fact an entirely new identity that has been associated with you, and is limited in what it's useful for.
Other examples of fictional identities include:
- The country you live in
- Your social media persona
- Your mortgage
- Geographical coordinates
- A moment in time
- A chess piece
Some of these identites are inert, for example points in space and time. Other identies have agency and so are able to act in the world - even as fictional concepts. In order to do this, they must "authenticate" themselves (which means "to prove they are real"), and act within a system of established rules.
For example, your D&D character exists only within the collective fiction of your D&D group, and can do anything the rules say. Its identity is authenticated simply by your claim as a member of the group that your character in fact exists. Similarly, a lawyer must prove they are a member of the Bar Association before they are allowed to practice law within that collective fiction.
"Cryptographic identity" is simply another way of authenticating a fictional identity within a given system. As we'll see, it has some interesting attributes that set it apart from things like a library card or your latitude and longitude. Before we get there though, let's look in more detail at how identities are authenticated.
Certificates
Merriam-Webster defines the verb "certify" as meaning "to attest authoritatively". A "certificate" is just a fancy way of saying "because I said so". Certificates are issued by a "certificate authority", someone who has the authority to "say so". Examples include your boss, your mom, or the Pope.
This method of authentication is how almost every institution authenticates the people who associate with it. Colleges issue student ID cards, governments issue passports, and websites allow you to "register an account".
In every case mentioned above, the "authority" creates a closed system in which a document (aka a "certificate") is issued which serves as a claim to a given identity. When someone wants to access some privileged service, location, or information, they present their certificate. The authority then validates it and grants or denies access. In the case of an international airport, the certificate is a little book printed with fancy inks. In the case of a login page, the certificate is a username and password combination.
This pattern for authentication is ubiquitous, and has some very important implications.
First of all, certified authentication implies that the issuer of the certificate has the right to exclusive control of any identity it issues. This identity can be revoked at any time, or its permissions may change. Your social credit score may drop arbitrarily, or money might disappear from your account. When dealing with certificate authorities, you have no inherent rights.
Second, certified authentication depends on the certificate authority continuing to exist. If you store your stuff at a storage facility but the company running it goes out of business, your stuff might disappear along with it.
Usually, authentication via certificate authority works pretty well, since an appeal can always be made to a higher authority (nature, God, the government, etc). Authorities also can't generally dictate their terms with impunity without losing their customers, alienating their constituents, or provoking revolt. But it's also true that certification by authority creates an incentive structure that frequently leads to abuse - arbitrary deplatforming is increasingly common, and the bigger the certificate authority, the less recourse the certificate holder (or "subject") has.
Certificates also put the issuer in a position to intermediate relationships that wouldn't otherwise be subject to their authority. This might take the form of selling user attention to advertisers, taking a cut of financial transactions, or selling surveillance data to third parties.
Proliferation of certificate authorities is not a solution to these problems. Websites and apps frequently often offer multiple "social sign-in" options, allowing their users to choose which certificate authority to appeal to. But this only piles more value into the social platform that issues the certificate - not only can Google shut down your email inbox, they can revoke your ability to log in to every website you used their identity provider to get into.
In every case, certificate issuance results in an asymmetrical power dynamic, where the issuer is able to exert significant control over the certificate holder, even in areas unrelated to the original pretext for the relationship between parties.
Self-Certification
But what if we could reverse this power dynamic? What if individuals could issue their own certificates and force institutions to accept them?

Ron Swanson's counterexample notwithstanding, there's a reason I can't simply write myself a parking permit and slip it under the windshield wiper. Questions about voluntary submission to legitimate authorities aside, the fact is that we don't have the power to act without impunity - just like any other certificate authority, we have to prove our claims either by the exercise of raw power or by appeal to a higher authority.
So the question becomes: which higher authority can we appeal to in order to issue our own certificates within a given system of identity?
The obvious answer here is to go straight to the top and ask God himself to back our claim to self-sovereignty. However, that's not how he normally works - there's a reason they call direct acts of God "miracles". In fact, Romans 13:1 explicitly says that "the authorities that exist have been appointed by God". God has structured the universe in such a way that we must appeal to the deputies he has put in place to govern various parts of the world.
Another tempting appeal might be to nature - i.e. the material world. This is the realm in which we most frequently have the experience of "self-authenticating" identities. For example, a gold coin can be authenticated by biting it or by burning it with acid. If it quacks like a duck, walks like a duck, and looks like a duck, then it probably is a duck.
In most cases however, the ability to authenticate using physical claims depends on physical access, and so appeals to physical reality have major limitations when it comes to the digital world. Captchas, selfies and other similar tricks are often used to bridge the physical world into the digital, but these are increasingly easy to forge, and hard to verify.
There are exceptions to this rule - an example of self-certification that makes its appeal to the physical world is that of a signature. Signatures are hard to forge - an incredible amount of data is encoded in physical signatures, from strength, to illnesses, to upbringing, to personality. These can even be scanned and used within the digital world as well. Even today, most contracts are sealed with some simulacrum of a physical signature. Of course, this custom is quickly becoming a mere historical curiosity, since the very act of digitizing a signature makes it trivially forgeable.
So: transcendent reality is too remote to subtantiate our claims, and the material world is too limited to work within the world of information. There is another aspect of reality remaining that we might appeal to: information itself.
Physical signatures authenticate physical identities by encoding unique physical data into an easily recognizable artifact. To transpose this idea to the realm of information, a "digital signature" might authenticate "digital identities" by encoding unique "digital data" into an easily recognizable artifact.
Unfortunately, in the digital world we have the additional challenge that the artifact itself can be copied, undermining any claim to legitimacy. We need something that can be easily verified and unforgeable.
Digital Signatures
In fact such a thing does exist, but calling it a "digital signature" obscures more than it reveals. We might just as well call the thing we're looking for a "digital fingerprint", or a "digital electroencephalogram". Just keep that in mind as we work our way towards defining the term - we are not looking for something looks like a physical signature, but for something that does the same thing as a physical signature, in that it allows us to issue ourselves a credential that must be accepted by others by encoding privileged information into a recognizable, unforgeable artifact.
With that, let's get into the weeds.
An important idea in computer science is that of a "function". A function is a sort of information machine that converts data from one form to another. One example is the idea of "incrementing" a number. If you increment 1, you get 2. If you increment 2, you get 3. Incrementing can be reversed, by creating a complementary function that instead subtracts 1 from a number.
A "one-way function" is a function that can't be reversed. A good example of a one-way function is integer rounding. If you round a number and get
5, what number did you begin with? It's impossible to know - 5.1, 4.81, 5.332794, in fact an infinite number of numbers can be rounded to the number5. These numbers can also be infinitely long - for example rounding PI to the nearest integer results in the number3.A real-life example of a useful one-way function is
sha256. This function is a member of a family of one-way functions called "hash functions". You can feed as much data as you like intosha256, and you will always get 256 bits of information out. Hash functions are especially useful because collisions between outputs are very rare - even if you change a single bit in a huge pile of data, you're almost certainly going to get a different output.Taking this a step further, there is a whole family of cryptographic one-way "trapdoor" functions that act similarly to hash functions, but which maintain a specific mathematical relationship between the input and the output which allows the input/output pair to be used in a variety of useful applications. For example, in Elliptic Curve Cryptography, scalar multiplication on an elliptic curve is used to derive the output.
"Ok", you say, "that's all completely clear and lucidly explained" (thank you). "But what goes into the function?" You might expect that because of our analogy to physical signatures we would have to gather an incredible amount of digital information to cram into our cryptographic trapdoor function, mashing together bank statements, a record of our heartbeat, brain waves and cellular respiration. Well, we could do it that way (maybe), but there's actually a much simpler solution.
Let's play a quick game. What number am I thinking of? Wrong, it's 82,749,283,929,834. Good guess though.
The reason we use signatures to authenticate our identity in the physical world is not because they're backed by a lot of implicit physical information, but because they're hard to forge and easy to validate. Even so, there is a lot of variation in a single person's signature, even from one moment to the next.
Trapdoor functions solve the validation problem - it's trivially simple to compare one 256-bit number to another. And randomness solves the problem of forgeability.
Now, randomness (A.K.A. "entropy") is actually kind of hard to generate. Random numbers that don't have enough "noise" in them are known as "pseudo-random numbers", and are weirdly easy to guess. This is why Cloudflare uses a video stream of their giant wall of lava lamps to feed the random number generator that powers their CDN. For our purposes though, we can just imagine that our random numbers come from rolling a bunch of dice.
To recap, we can get a digital equivalent of a physical signature (or fingerprint, etc) by 1. coming up with a random number, and 2. feeding it into our chosen trapdoor function. The random number is called the "private" part. The output of the trapdoor function is called the "public" part. These two halves are often called "keys", hence the terms "public key" and "private key".
And now we come full circle - remember about 37 years ago when I introduced the term "cryptographic identity"? Well, we've finally arrived at the point where I explain what that actually is.
A "cryptographic identity" is identified by a public key, and authenticated by the ability to prove that you know the private key.
Notice that I didn't say "authenticated by the private key". If you had to reveal the private key in order to prove you know it, you could only authenticate a public key once without losing exclusive control of the key. But cryptographic identities can be authenticated any number of times because the certification is an algorithm that only someone who knows the private key can execute.
This is the super power that trapdoor functions have that hash functions don't. Within certain cryptosystems, it is possible to mix additional data with your private key to get yet another number in such a way that someone else who only knows the public key can prove that you know the private key.
For example, if my secret number is
12, and someone tells me the number37, I can "combine" the two by adding them together and returning the number49. This "proves" that my secret number is12. Of course, addition is not a trapdoor function, so it's trivially easy to reverse, which is why cryptography is its own field of knowledge.What's it for?
If I haven't completely lost you yet, you might be wondering why this matters. Who cares if I can prove that I made up a random number?
To answer this, let's consider a simple example: that of public social media posts.
Most social media platforms function by issuing credentials and verifying them based on their internal database. When you log in to your Twitter (ok, fine, X) account, you provide X with a phone number (or email) and password. X compares these records to the ones stored in the database when you created your account, and if they match they let you "log in" by issuing yet another credential, called a "session key".
Next, when you "say" something on X, you pass along your session key and your tweet to X's servers. They check that the session key is legit, and if it is they associate your tweet with your account's identity. Later, when someone wants to see the tweet, X vouches for the fact that you created it by saying "trust me" and displaying your name next to the tweet.
In other words, X creates and controls your identity, but they let you use it as long as you can prove that you know the secret that you agreed on when you registered (by giving it to them every time).
Now pretend that X gets bought by someone even more evil than Elon Musk (if such a thing can be imagined). The new owner now has the ability to control your identity, potentially making it say things that you didn't actually say. Someone could be completely banned from the platform, but their account could be made to continue saying whatever the owner of the platform wanted.
In reality, such a breach of trust would quickly result in a complete loss of credibility for the platform, which is why this kind of thing doesn't happen (at least, not that we know of).
But there are other ways of exploiting this system, most notably by censoring speech. As often happens, platforms are able to confiscate user identities, leaving the tenant no recourse except to appeal to the platform itself (or the government, but that doesn't seem to happen for some reason - probably due to some legalese in social platforms' terms of use). The user has to start completely from scratch, either on the same platform or another.
Now suppose that when you signed up for X instead of simply telling X your password you made up a random number and provided a cryptographic proof to X along with your public key. When you're ready to tweet (there's no need to issue a session key, or even to store your public key in their database) you would again prove your ownership of that key with a new piece of data. X could then publish that tweet or not, along with the same proof you provided that it really came from you.
What X can't do in this system is pretend you said something you didn't, because they don't know your private key.
X also wouldn't be able to deplatform you as effectively either. While they could choose to ban you from their website and refuse to serve your tweets, they don't control your identity. There's nothing they can do to prevent you from re-using it on another platform. Plus, if the system was set up in such a way that other users followed your key instead of an ID made up by X, you could switch platforms and keep your followers. In the same way, it would also be possible to keep a copy of all your tweets in your own database, since their authenticity is determined by your digital signature, not X's "because I say so".
This new power is not just limited to social media either. Here are some other examples of ways that self-issued cryptographic identites transform the power dynamic inherent in digital platforms:
- Banks sometimes freeze accounts or confiscate funds. If your money was stored in a system based on self-issued cryptographic keys rather than custodians, banks would not be able to keep you from accessing or moving your funds. This system exists, and it's called bitcoin.
- Identity theft happens when your identifying information is stolen and used to take out a loan in your name, and without your consent. The reason this is so common is because your credentials are not cryptographic - your name, address, and social security number can only be authenticated by being shared, and they are shared so often and with so many counterparties that they frequently end up in data breaches. If credit checks were authenticated by self-issued cryptographic keys, identity theft would cease to exist (unless your private key itself got stolen).
- Cryptographic keys allow credential issuers to protect their subjects' privacy better too. Instead of showing your ID (including your home address, birth date, height, weight, etc), the DMV could sign a message asserting that the holder of a given public key indeed over 21. The liquor store could then validate that claim, and your ownership of the named key, without knowing anything more about you. Zero-knowledge proofs take this a step further.
In each of these cases, the interests of the property owner, loan seeker, or customer are elevated over the interests of those who might seek to control their assets, exploit their hard work, or surveil their activity. Just as with personal privacy, freedom of speech, and Second Amendment rights the individual case is rarely decisive, but in the aggregate realigned incentives can tip the scale in favor of freedom.
Objections
Now, there are some drawbacks to digital signatures. Systems that rely on digital signatures are frequently less forgiving of errors than their custodial counterparts, and many of their strengths have corresponding weaknesses. Part of this is because people haven't yet developed an intuition for how to use cryptographic identities, and the tools for managing them are still being designed. Other aspects can be mitigated through judicious use of keys fit to the problems they are being used to solve.
Below I'll articulate some of these concerns, and explore ways in which they might be mitigated over time.
Key Storage
Keeping secrets is hard. "A lie can travel halfway around the world before the truth can get its boots on", and the same goes for gossip. Key storage has become increasingly important as more of our lives move online, to the extent that password managers have become almost a requirement for keeping track of our digital lives. But even with good password management, credentials frequently end up for sale on the dark web as a consequence of poorly secured infrastructure.
Apart from the fact that all of this is an argument for cryptographic identities (since keys are shared with far fewer parties), it's also true that the danger of losing a cryptographic key is severe, especially if that key is used in multiple places. Instead of hackers stealing your Facebook password, they might end up with access to all your other social media accounts too!
Keys should be treated with the utmost care. Using password managers is a good start, but very valuable keys should be stored even more securely - for example in a hardware signing device. This is a hassle, and something additional to learn, but is an indispensable part of taking advantage of the benefits associated with cryptographic identity.
There are ways to lessen the impact of lost or stolen secrets, however. Lots of different techniques exist for structuring key systems in such a way that keys can be protected, invalidated, or limited. Here are a few:
- Hierarchical Deterministic Keys allow for the creation of a single root key from which multiple child keys can be generated. These keys are hard to link to the parent, which provides additional privacy, but this link can also be proven when necessary. One limitation is that the identity system has to be designed with HD keys in mind.
- Key Rotation allows keys to become expendable. Additional credentials might be attached to a key, allowing the holder to prove they have the right to rotate the key. Social attestations can help with the process as well if the key is embedded in a web of trust.
- Remote Signing is a technique for storing a key on one device, but using it on another. This might take the form of signing using a hardware wallet and transferring an SD card to your computer for broadcasting, or using a mobile app like Amber to manage sessions with different applications.
- Key sharding takes this to another level by breaking a single key into multiple pieces and storing them separately. A coordinator can then be used to collaboratively sign messages without sharing key material. This dramatically reduces the ability of an attacker to steal a complete key.
Multi-Factor Authentication
One method for helping users secure their accounts that is becoming increasingly common is "multi-factor authentication". Instead of just providing your email and password, platforms send a one-time use code to your phone number or email, or use "time-based one time passwords" which are stored in a password manager or on a hardware device.
Again, MFA is a solution to a problem inherent in account-based authentication which would not be nearly so prevalent in a cryptographic identity system. Still, theft of keys does happen, and so MFA would be an important improvement - if not for an extra layer of authentication, then as a basis for key rotation.
In a sense, MFA is already being researched - key shards is one way of creating multiple credentials from a single key. However, this doesn't address the issue of key rotation, especially when an identity is tied to the public key that corresponds to a given private key. There are two possible solutions to this problem:
- Introduce a naming system. This would allow identities to use a durable name, assigning it to different keys over time. The downside is that this would require the introduction of either centralized naming authorities (back to the old model), or a blockchain in order to solve Zooko's trilemma.
- Establish a chain of keys. This would require a given key to name a successor key in advance and self-invalidate, or some other process like social recovery to invalidate an old key and assign the identity to a new one. This also would significantly increase the complexity of validating messages and associating them with a given identity.
Both solutions are workable, but introduce a lot of complexity that could cause more trouble than it's worth, depending on the identity system we're talking about.
Surveillance
One of the nice qualities that systems based on cryptographic identities have is that digitally signed data can be passed through any number of untrusted systems and emerge intact. This ability to resist tampering makes it possible to broadcast signed data more widely than would otherwise be the case in a system that relies on a custodian to authenticate information.
The downside of this is that more untrusted systems have access to data. And if information is broadcast publicly, anyone can get access to it.
This problem is compounded by re-use of cryptographic identities across multiple contexts. A benefit of self-issued credentials is that it becomes possible to bring everything attached to your identity with you, including social context and attached credentials. This is convenient and can be quite powerful, but it also means that more context is attached to your activity, making it easier to infer information about you for advertising or surveillance purposes. This is dangerously close to the dystopian ideal of a "Digital ID".
The best way to deal with this risk is to consider identity re-use an option to be used when desirable, but to default to creating a new key for every identity you create. This is no worse than the status quo, and it makes room for the ability to link identities when desired.
Another possible approach to this problem is to avoid broadcasting signed data when possible. This could be done by obscuring your cryptographic identity when data is served from a database, or by encrypting your signed data in order to selectively share it with named counterparties.
Still, this is a real risk, and should be kept in mind when designing and using systems based on cryptographic identity. If you'd like to read more about this, please see this blog post.
Making Keys Usable
You might be tempted to look at that list of trade-offs and get the sense that cryptographic identity is not for mere mortals. Key management is hard, and footguns abound - but there is a way forward. With nostr, some new things are happening in the world of key management that have never really happened before.
Plenty of work over the last 30 years has gone into making key management tractable, but none have really been widely adopted. The reason for this is simple: network effect.
Many of these older key systems only applied the thinnest veneer of humanity over keys. But an identity is much richer than a mere label. Having a real name, social connections, and a corpus of work to attach to a key creates a system of keys that humans care about.
By bootstrapping key management within a social context, nostr ensures that the payoff of key management is worth the learning curve. Not only is social engagement a strong incentive to get off the ground, people already on the network are eager to help you get past any roadblocks you might face.
So if I could offer an action item: give nostr a try today. Whether you're in it for the people and their values, or you just want to experiment with cryptographic identity, nostr is a great place to start. For a quick introduction and to securely generate keys, visit njump.me.
Thanks for taking the time to read this post. I hope it's been helpful, and I can't wait to see you on nostr!
-
 @ 8f69ac99:4f92f5fd
2025-02-27 12:47:01
@ 8f69ac99:4f92f5fd
2025-02-27 12:47:01O Estado Social tem sido um pilar das políticas sociais europeias há décadas, oferecendo uma rede de segurança aos cidadãos através de diversos programas governamentais. Contudo, com a evolução das economias e o envelhecimento da população a pressionar os recursos públicos, este modelo tradicional enfrenta desafios crescentes. Custos em alta, ineficiências burocráticas e efeitos indesejados têm gerado um debate cada vez mais intenso sobre a sua sustentabilidade. Como alternativa, o Rendimento Básico Universal (RBU) ganhou destaque, prometendo simplicidade, mas trazendo preocupações quanto ao custo e aos desincentivos ao trabalho. Há, porém, uma opção mais equilibrada que merece atenção: o Imposto sobre o Rendimento Negativo (IRN).
Diferente da assistência social convencional, o IRN oferece apoio financeiro a quem está abaixo de um limiar de rendimento definido, sem exigir que procurem emprego ou dependam de ajudas públicas. Ao reduzir gradualmente os subsídios à medida que os rendimentos aumentam, incentiva a produtividade e preserva a iniciativa pessoal. Neste artigo, vamos explorar o IRN em profundidade, destacando as suas vantagens sobre os sistemas tradicionais, abordando as falhas do RBU e avaliando o seu potencial como uma reforma transformadora na Europa. Num contexto de mudanças económicas e demográficas, o IRN surge como um caminho prático para um sistema que equilibre apoio, dignidade e sustentabilidade.
Problemas dos Sistemas Tradicionais de Assistência Social
O Estado Social tradicional, embora bem-intencionado, tem sido alvo de críticas crescentes pelas suas ineficiências e consequências inesperadas.
Ineficiência e Burocracia
Estruturas administrativas complexas frequentemente atrasam os sistemas de assistência social, levando a desperdícios de recursos. Programas sobrepostos e serviços redundantes aumentam os custos, sobrecarregando os contribuintes. Por exemplo, várias entidades podem oferecer benefícios semelhantes, enquanto processos morosos atrasam a ajuda a quem precisa. Com o envelhecimento da população europeia a exigir mais apoio, estas ineficiências põem em risco a estabilidade financeira, desafiando os decisores políticos a repensarem a distribuição de recursos.
Incentivos Perversos
A assistência social pode, sem querer, desencorajar o trabalho e perpetuar a dependência. Surgem "armadilhas de assistência" quando os benefícios são estruturados de forma a que ganhar um salário resulte numa redução abrupta da ajuda, tornando o emprego menos atractivo do que permanecer no assistencialismo. Isso cria um ciclo em que os beneficiários hesitam em procurar trabalho ou formação, comprometendo as suas perspectivas a longo prazo. Com o tempo, tais sistemas arriscam criar uma cultura de dependência, minando a iniciativa pessoal e prendendo indivíduos numa estagnação económica.
Peso Económico
A pressão financeira do Estado Social está a intensificar-se com as mudanças demográficas na Europa. Populações mais envelhecidas requerem maior apoio, elevando os custos e exigindo impostos mais altos ou gastos públicos acrescidos. Isso desvia recursos da inovação e do investimento, podendo travar o crescimento económico. Sem reformas, estas despesas crescentes podem tornar-se insustentáveis, obrigando os governos a encontrar soluções que mantenham o apoio sem comprometer as finanças.
Estigma Social
Além das questões económicas, a assistência social traz muitas vezes um custo social. Os beneficiários enfrentam frequentemente estereótipos de preguiça ou incompetência, o que gera vergonha e diminui a autoestima. Este estigma pode dificultar a mobilidade social, tornando mais complicado sair da dependência. Resolver isto exige um sistema que não só apoie, mas também capacite, reduzindo preconceitos e promovendo inclusão.
Face a estas falhas, a Europa precisa de explorar alternativas que prestem ajuda de forma mais eficaz. O Imposto sobre o Rendimento Negativo apresenta-se como uma opção promissora, capaz de enfrentar estas questões sistémicas.
O Caso Contra o Rendimento Básico Universal (RBU)
O Rendimento Básico Universal surgiu como uma ideia ousada para combater a pobreza e a desigualdade, oferecendo a cada cidadão um pagamento fixo independentemente das suas necessidades. No entanto, a sua simplicidade traz desvantagens significativas.
O custo do RBU é um obstáculo enorme. Implementá-lo em toda a Europa exigiria fundos avultados, pressionando orçamentos já sobrecarregados pelos compromissos actuais do Estado Social. Isso poderia implicar subidas acentuadas de impostos ou cortes noutros serviços, enquanto a criação da infraestrutura administrativa necessária traria mais despesas. Há também quem tema os desincentivos ao trabalho: se todos receberem o mesmo valor, alguns podem sentir menos motivação para trabalhar ou arriscar em projectos empreendedores, podendo afectar a vitalidade económica.
Além disso, a abordagem universal do RBU sacrifica eficiência. Ao distribuir fundos de forma igual, não dá prioridade a quem mais precisa, entregando recursos aos mais ricos enquanto dilui o impacto sobre os pobres. Esta falta de foco levanta dúvidas sobre a sua capacidade de combater a desigualdade de forma eficaz. Embora o apelo do RBU esteja na sua universalidade, estes desafios apontam para a necessidade de uma solução mais direccionada—e é aqui que o IRN entra em cena.
Compreender o Imposto sobre o Rendimento Negativo (IRN)
O Imposto sobre o Rendimento Negativo propõe uma abordagem refinada ao apoio social, combinando assistência com incentivos. No seu cerne, define um limiar de rendimento base—digamos, 1.000 euros por mês. Quem ganha menos recebe um subsídio proporcional à diferença, enquanto quem ultrapassa esse valor paga impostos para financiar o sistema. Por exemplo, com uma taxa de subsídio de 50%, quem não tem rendimentos recebe 500 euros, e quem ganha 400 euros recebe 300 euros, elevando o total para 700 euros. À medida que o rendimento se aproxima do limiar, o subsídio diminui, desaparecendo nos 1.000 euros, altura em que a tributação começa.
Veja-se uma ilustração simples:
| Rendimento Mensal (€) | Pagamento IRN (€) | Rendimento Total Após IRN (€) | |-----------------------|-------------------|------------------------------| | 0 | 500 | 500 | | 400 | 300 | 700 | | 800 | 100 | 900 | | 1.000 | 0 | 1.000 | | 1.200 | - (impostos aplicam-se) | 1.200 - impostos |
Isto garante que trabalhar compensa sempre: ganhar mais aumenta o rendimento total, evitando a armadilha da assistência. O financiamento vem de um imposto fixo—talvez 19%—sobre os rendimentos acima do limiar. Quem ganha 1.500 euros, por exemplo, paga 95 euros sobre os 500 euros acima de 1.000, ficando com 1.405 euros. Este modelo fiscal simples facilita a gestão e assegura equidade.
| Rendimento (€) | Rendimento Tributável (€) | Imposto (€) | Após Imposto (€) | |----------------|---------------------|---------|------------------| | 1000 | 0 | 0 | 1000 | | 1200 | 200 | 38 | 1162 | | 2000 | 1000 | 190 | 1810 |
O IRN pode ser de participação voluntária, através de um contrato. As pessoas podem aderir ao sistema se precisarem de apoio ou rejeitá-lo se não aceitarem ajuda estatal, evitando os impostos associados ao financiamento do IRN. Quem optar por sair pode reentrar em caso de dificuldades, equilibrando liberdade de escolha com pragmatismo. Para libertários desconfiados de ingerências governamentais, isto torna o IRN um compromisso—um passo para longe do assistencialismo coercivo e em direcção a maior autonomia.
Filosoficamente, o IRN não é um objectivo final, mas uma ponte. Ao simplificar a ajuda e reduzir a burocracia, pode abrir caminho para soluções privadas, como caridade ou apoio mútuo, diminuindo o papel do estado ao longo do tempo. Características como a avaliação de meios e a indexação à inflação reforçam a sua adaptabilidade, garantindo que o apoio permaneça justo e relevante.
Vantagens do Imposto sobre o Rendimento Negativo (IRN)
O IRN destaca-se onde o Estado Social tradicional falha. Os seus subsídios decrescentes incentivam o trabalho, premiando o esforço à medida que o rendimento sobe e impulsionando a produtividade. Isto contrasta fortemente com as armadilhas da assistência, encorajando as pessoas a procurarem formação ou a arriscarem em empreendedorismo sem medo de perder apoio de repente.
Na gestão, o IRN é revolucionário. Substituir um emaranhado de programas por um único sistema reduz a burocracia e os custos, canalizando recursos directamente para quem precisa. Um processo de pagamento único elimina sobreposições, tornando a entrega de ajuda mais rápida e eficiente.
A dignidade é outro ponto forte. Ao oferecer escolha e evitar supervisão intrusiva, o IRN escapa ao estigma do assistencialismo, dando aos beneficiários autonomia para gerir as suas finanças. Isso promove o autorrespeito e um sentido de controlo, quebrando o ciclo de dependência.
Economicamente, a flexibilidade do IRN sobressai. Adapta-se às flutuações de rendimento, direccionando a ajuda exactamente onde é necessária. Estudos indicam que pode reduzir a pobreza, melhorar a mobilidade social e até beneficiar a saúde, ao aliviar o stress financeiro, oferecendo um impulso abrangente ao bem-estar.
Responder às Críticas ao Imposto sobre o Rendimento Negativo (IRN)
Nenhuma política escapa a críticas, e o IRN tem as suas. Os libertários veem, e bem, os impostos como roubo, e embora o IRN não elimine esta tensão, suaviza-a. Ao condensar o Estado Social num sistema claro e simples, reduz a intromissão estatal face à burocracia actual. Os seus incentivos ao trabalho alinham-se com valores de responsabilidade, tornando-o um passo aceitável a curto prazo.
O financiamento preocupa, sobretudo em países europeus já muito tributados, mas uma taxa fixa oferece uma solução. Simples e previsível, minimiza os custos administrativos e assegura contribuições justas, sustentando o IRN sem sobrecarga excessiva. Há também quem debata o seu impacto social—uns chamam-lhe um subsídio fácil, um hand-out, outros um sistema demasiado voltado para o mercado. Ainda assim, o IRN encontra um meio-termo, oferecendo uma rede de segurança que recompensa o esforço sem controlar vidas.
Passar para o IRN exige eliminar gradualmente os programas antigos e informar o público sobre os seus benefícios: um governo mais leve, menos dependência e maior iniciativa pessoal. Para quem sonha com um futuro sem estado, o IRN não é o destino, mas um movimento prático rumo a sistemas de apoio voluntários, promovendo uma cultura de autossuficiência.
Conclusão
O Imposto sobre o Rendimento Negativo não é perfeito, mas é um avanço claro face ao status quo. Reduz os excessos do Estado Social, promove trabalho e dignidade, e oferece à Europa uma reforma viável perante as pressões económicas. Para os contribuintes, promete eficiência; para os beneficiários, oportunidade. Numa região onde o assistencialismo está profundamente enraizado, o IRN surge como um passo ousado, mas possível, para um futuro mais livre e sustentável—um que capacite as pessoas enquanto alivia o peso do estado.
Photo by The New York Public Library on Unsplash
-
 @ e968e50b:db2a803a
2024-08-12 16:50:52
@ e968e50b:db2a803a
2024-08-12 16:50:52...a 25W light bulb. Sorry. But is anybody working on this (using mining heat and a lower watt LED bulb)? I know that GekkoScience is working on a coffee warmer right now.
originally posted at https://stacker.news/items/645846
-
 @ 57d1a264:69f1fee1
2024-08-12 15:45:48
@ 57d1a264:69f1fee1
2024-08-12 15:45:48Zap this meme for today (Special Edition) Meme Monday contest
originally posted at https://stacker.news/items/645734
-
 @ a5ee4475:2ca75401
2025-05-19 01:11:59
@ a5ee4475:2ca75401
2025-05-19 01:11:59clients #link #list #english #article #finalversion #descentralismo
*These clients are generally applications on the Nostr network that allow you to use the same account, regardless of the app used, keeping your messages and profile intact.
**However, you may need to meet certain requirements regarding access and account NIP for some clients, so that you can access them securely and use their features correctly.
CLIENTS
Twitter like
- Nostrmo - [source] 🌐💻(🐧🪟🍎)🍎🤖(on zapstore)
- Coracle - Super App [source] 🌐🤖(on zapstore)
- Amethyst - Super App with note edit, delete and other stuff with Tor [source] 🤖(on zapstore)
- Primal - Social and wallet [source] 🌐🍎🤖(on zapstore)
- Iris - [source] 🌐🤖🍎
- Current - [source] 🤖🍎
- FreeFrom 🤖🍎
- Openvibe - Nostr and others (new Plebstr) [source] 🤖🍎
- Snort 🌐(🤖[early access]) [onion] [source]
- Damus 🍎 [source]
- Nos 🍎 [source]
- Nostur 🍎 [source]
- NostrBand 🌐 [info] [source]
- Yana [source] 🌐💻(🐧) 🍎🤖(on zapstore)
- Nostribe [on development] 🌐 [source]
- Lume 💻(🐧🪟🍎) [info] [source]
- Gossip - [source] 💻(🐧🪟🍎)
- noStrudel - Gamified Experience [onion] [info/source] 🌐
- [Nostrudel Next] - [onion]
- moStard - Nostrudel with Monero [onion] [info/source] 🌐
- Camelus - [source] 🤖 [early access]
Community
- CCNS - Community Curated Nostr Stuff [source]
- Nostr Kiwi [creator] 🌐
- Satellite [info] 🌐
- Flotilla - [source] 🌐🐧🤖(on zapstore)
- Chachi - [source] 🌐
- Futr - Coded in haskell [source] 🐧 (others soon)
- Soapbox - Comunnity server [info] [source] 🌐
- Ditto - Soapbox community server 🌐 [source] 🌐
- Cobrafuma - Nostr brazilian community on Ditto [info] 🌐
- Zapddit - Reddit like [source] 🌐
- Voyage (Reddit like) [on development] 🤖
Wiki
- Wikifreedia - Wiki Dark mode [source] 🌐
- Wikinostr - Wiki with tabs clear mode [source] 🌐
- Wikistr - Wiki clear mode [info] [source] 🌐
Search
- Keychat - Signal-like chat with AI and browser [source] 💻(🐧🪟🍎) - 📱(🍎🤖{on zapstore})
- Spring - Browser for Nostr apps and other sites [source] 🤖 (on zapstore)
- Advanced nostr search - Advanced note search by isolated terms related to a npub profile [source] 🌐
- Nos Today - Global note search by isolated terms [info] [source] 🌐
- Nostr Search Engine - API for Nostr clients [source]
- Ntrends - Trending notes and profiles 🌐
Website
- Nsite - Nostr Site [onion] [info] [source]
- Nsite Gateway - Nostr Site Gateway [source]
- Npub pro - Your site on Nostr [source]
App Store
ZapStore - Permitionless App Store [source] 🤖 💻(🐧🍎)
Video and Live Streaming
- Flare - Youtube like 🌐 [source]
- ZapStream - Lives, videos, shorts and zaps (NIP-53) [source] 🌐 🤖(lives only | Amber | on zapstore)
- Swae - Live streaming [source] (on development) ⏳
Post Aggregator - Kinostr - Nostr Cinema with #kinostr [english] [author] 🌐 - Stremstr - Nostr Cinema with #kinostr [english] [source] 📱 (on development) ⏳
Link Agreggator - Kinostr - #kinostr - Nostr Cinema Profile with links [English] - Equinox - Nostr Cinema Community with links [Portuguese]
Audio and Podcast Transmission
- Castr - Your npub as podcast feed [source]
- Nostr Nests - Audio Chats [source] 🌐
- Fountain - Podcast [source] 🤖🍎
- Corny Chat - Audio Chat [source] 🌐
Music
- Tidal - Music Streaming [source] [about] [info] 🤖🍎🌐
- Wavlake - Music Streaming [source] 🌐(🤖🍎 [early access])
- Tunestr - Musical Events [source] [about] 🌐
- Stemstr - Musical Colab (paid to post) [source] [about] 🌐
Images
- Lumina - Trending images and pictures [source] 🌐
- Pinstr - Pinterest like [source] 🌐
- Slidestr - DeviantArt like [source] 🌐
- Memestr - ifunny like [source] 🌐
Download and Upload
Documents, graphics and tables
- Mindstr - Mind maps [source] 🌐
- Docstr - Share Docs [info] [source] 🌐
- Formstr - Share Forms [info] 🌐
- Sheetstr - Share Spreadsheets [source] 🌐
- Slide Maker - Share slides 🌐 [Advice: Slide Maker https://zaplinks.lol/ site is down]
Health
- Sobrkey - Sobriety and mental health [source] 🌐
- Runstr - Running app [source] 🌐
- NosFabrica - Finding ways for your health data 🌐
- LazerEyes - Eye prescription by DM [source] 🌐
Forum
- OddBean - Hacker News like [info] [source] 🌐
- LowEnt - Forum [info] 🌐
- Swarmstr - Q&A / FAQ [info] 🌐
- Staker News - Hacker News like 🌐 [info]
Direct Messenges (DM)
- 0xchat 🤖🍎 [source]
- Nostr Chat 🌐🍎 [source]
- Blowater 🌐 [source]
- Anigma (new nostrgram) - Telegram based [on development] [source]
Reading
- Oracolo - A minimalist Nostr html blog [source]
- nRSS - Nostr RSS reader 🌐
- Highlighter - Insights with a highlighted read [info] 🌐
- Zephyr - Calming to Read [info] 🌐
- Flycat - Clean and Healthy Feed [info] 🌐
- Nosta - Check Profiles [on development] [info] 🌐
- Alexandria - e-Reader and Nostr Knowledge Base (NKB) [source] 🌐
Writing
- Habla - Blog [info] 🌐
- Blogstack - Blog [info]🌐
- YakiHonne - Articles and News [info] 🌐🍎🤖(on zapstore)
Lists
- Following - Users list [source] 🌐
- Nostr Unfollower - Nostr Unfollower
- Listr - Lists [source] 🌐
- Nostr potatoes - Movies List [source] 💻(numpy)
Market and Jobs
- Shopstr - Buy and Sell [onion] [source] 🌐
- Nostr Market - Buy and Sell 🌐
- Plebeian Market - Buy and Sell [source] 🌐
- Ostrich Work - Jobs [source] 🌐
- Nostrocket - Jobs [source] 🌐
Data Vending Machines - DVM (NIP90)
(Data-processing tools)
Games
- Chesstr - Chess 🌐 [source]
- Jestr - Chess [source] 🌐
- Snakestr - Snake game [source] 🌐
- Snakes on a Relay - Multiplayer Snake game like slither.io [source] 🌐
ENGINES - DEG Mods - Decentralized Game Mods [info] [source] 🌐 - NG Engine - Nostr Game Engine [source] 🌐 - JmonkeyEngine - Java game engine [source] 🌐
Customization
Like other Services
- Olas - Instagram like [source] 🌐🍎🤖(on zapstore)
- Nostree - Linktree like 🌐
- Rabbit - TweetDeck like [info] 🌐
- Zaplinks - Nostr links 🌐
- Omeglestr - Omegle-like Random Chats [source] 🌐
General Uses
- Njump - HTML text gateway source 🌐
- Filestr - HTML midia gateway [source] 🌐
- W3 - Nostr URL shortener [source] 🌐
- Playground - Test Nostr filters [source] 🌐
Places
- Wherostr - Travel and show where you are
- Arc Map (Mapstr) - Bitcoin Map [info]
Driver and Delivery
- RoadRunner - Uber like [on development] ⏱️
- Nostrlivery - iFood like [on development] ⏱️
⚠️ SCAM ⚠️ | Arcade City - Uber like [source]
OTHER STUFF
Lightning Wallets (zap)
- Alby - Native and extension [info] 🌐
- ZBD - Gaming and Social [info] [source] 🤖🍎
- Wallet of Satoshi - Simplest Lightning Wallet [info] 🤖🍎
- Minibits - Cashu mobile wallet [info] 🤖
- Blink - Opensource custodial wallet (KYC over 1000 usd) [source] 🤖🍎
- LNbits - App and extesion [source] 🤖🍎💻
- Zeus - [info] [source] 🤖🍎
Without Zap - Wassabi Wallet - Privacy-focused and non-custodial with Nostr Update Manager [source]
Exchange
Media Server (Upload Links)
audio, image and video
Connected with Nostr (NIP):
- Nostr Build - Free and paid Upload [info] [source] 🌐
- NostrMedia - Written in Go with Nip 96 / Blossom (free and paid) [info] [source]
- Nostr Check - [info] [source] 🌐
- NostPic - [info] [source] 🌐
- Sovbit - Free and paid upload [info] [source] 🌐
- Voidcat - Nip-96 and Blossom [source] 🌐
- Primal Media - Primal Media Uploader [source] 🌐
Blossom - Your Media Safer
- Primal Blossom 🌐
- NostrBuild Blossom - Free upload (max 100MiB) and paid [info] [source] 🌐
Paid Upload Only
- Satellite CDN - prepaid upload (max 5GB each) [info] [source] 🌐
Without Nostr NIP:
- Pomf - Upload larger videos (max 1GB) [source]
- Catbox - max 200 MB [source]
- x0 - max 512 MiB [source]
Donation and payments
- Zapper - Easy Zaps [source] 🌐
- Autozap [source] 🌐
- Zapmeacoffee 🌐
- Nostr Zap 💻(numpy)
- Creatr - Creators subscription 🌐
- Geyzer - Crowdfunding [info] [source] 🌐
- Heya! - Crowdfunding [source]
Security
- Secret Border - Generate offline keys 💻(java)
- Umbrel - Your private relay [source] 🌐
Key signing/login and Extension
- Amber - Key signing [source] 🤖(on zapstore)
- Nowser - Account access keys 📱(🤖🍎) 💻(🐧🍎🪟)
- Nos2x - Account access keys 🌐
- Nsec.app 🌐 [info]
- Lume - [info] [source] 🐧🪟🍎
- Satcom - Share files to discuss - [info] 🌐
- KeysBand - Multi-key signing [source] 🌐
Code
- Stacks - AI Templates [info] [source] 🌐
- Nostrify - Share Nostr Frameworks 🌐
- Git Workshop (github like) [experimental] 🌐
- Gitstr (github like) [on development] ⏱️
- Osty [on development] [info] 🌐
- Python Nostr - Python Library for Nostr
- Sybil - Creating, managing and test Nostr events [on development] ⏱️
Relay Check and Cloud
- Nostr Watch - See your relay speed 🌐
- NosDrive - Nostr Relay that saves to Google Drive
Bidges and Getways
- Matrixtr Bridge - Between Matrix & Nostr
- Mostr - Between Nostr & Fediverse
- Nostrss - RSS to Nostr
- Rsslay - Optimized RSS to Nostr [source]
- Atomstr - RSS/Atom to Nostr [source]
Useful Profiles and Trends
nostr-voice - Voice note (just some clients)
NOT RELATED TO NOSTR
Voca - Text-to-Speech App for GrapheneOS [source] 🤖(on zapstore)
Android Keyboards
Personal notes and texts
Front-ends
- Nitter - Twitter / X without your data [source]
- NewPipe - Youtube, Peertube and others, without account & your data [source] 🤖
- Piped - Youtube web without you data [source] 🌐
Other Services
- Brave - Browser [source]
- DuckDuckGo - Search [source]
- LLMA - Meta - Meta open source AI [source]
- DuckDuckGo AI Chat - Famous AIs without Login [source]
- Proton Mail - Mail [source]
Other open source index: Degoogled Apps
Some other Nostr index on:
-
 @ 4857600b:30b502f4
2025-02-20 19:09:11
@ 4857600b:30b502f4
2025-02-20 19:09:11Mitch McConnell, a senior Republican senator, announced he will not seek reelection.
At 83 years old and with health issues, this decision was expected. After seven terms, he leaves a significant legacy in U.S. politics, known for his strategic maneuvering.
McConnell stated, “My current term in the Senate will be my last.” His retirement marks the end of an influential political era.
-
 @ 3bf0c63f:aefa459d
2025-02-22 17:05:13
@ 3bf0c63f:aefa459d
2025-02-22 17:05:13P2Panda and the super-peer curse
Recently was suggested to me that https://p2panda.org/ was a great protocol and that maybe Nostr wouldn't be necessary if we could just use that. After making the blind remark that p2p doesn't work I was pointed to https://github.com/p2panda/aquadoggo which acts as a "node" in some ways similar to a "relay", and it all looks somewhat well, cool, maybe they're into something:

Then I realized that Aquadoggo isn't really a relay, it is more like an "app server". There are still no relays in the Nostr sense in p2panda, the base of communication is still p2p between "nodes", and, as Aquadoggo's readme say, it could be run both as a client and as a server. In other words, we could easily have an "Nostr Aquadoggo" that abstracts all communication with relays, relay selection, event and tag parsing and signatures then stores filtered, ordered, indexed data locally: it is just a Nostr client.
That you can put one of these in a server doesn't change that fact that it will be still a client -- and that underlings behind it consuming its API will be controlled, censored, mislead and tricked. This design that requires trust in one single server from a dumb client in exchange for massaged, sorted, filtered, ordered data is seen not only in p2panda, but it's also a fundamental part of the design in many of the supposed decentralized protocols out there, including Bluesky, Farcaster and Pubky. It has also found its way even into RSS, with feed aggregators, and into IRC with bouncers. It can also be seen being experimented with inside Nostr, with ZBD Social, Primal, Ditto, Satlantis and others I forgot, and even behind the ideas of some pseudo-relays like Bostr and filter.nostr.wine (although I'm not sure). Notably, though, this design is not a part of SSB or Mastodon and these two weren't ever corrupted by it as far as I know.
In any case, should we accept that such architecture will eventually find its way into Nostr and completely dominate it? If I believed the answer was "yes" I would immediately declare Nostr a failed experiment, but I don't. As the main author of one such experiment (ZBD Social), I still think this architecture isn't necessarily bad as long as it's limited and restricted to certain circumstances, but it does pose a risk of Nostr becoming almost as bad as Bluesky, so the path has to be threaded carefully.
Ultimately, though, what all these protocols are trying to achieve by injecting these dangerous super-peers into their architecture is the reliability that pure p2p cannot provide, along with filtering and discovery features. And Nostr's multi-relay architecture, as cumbersome and weird as it is, represents a very different approach to solving the same problems, one that none of these other protocols can even begin to consider emulating, and I believe we have to accept that, embrace it and lean on it more.
We can go there by having whitelisted relays as communities, relays that enforce group rules automatically, relays that provide fulltext search, relays that provide AI-based personalized custom feeds, relays that filter out reply spam or harassment (or enforce blocks at the server-side), relays that restrict reads to a certain selected group, relays that perform curation and make valuable content reemerge from the abyss of the ongoing stream; and of course clients that surface all these different types of relays and their features.
Why is this complex madness better than the super-peer architecture? Because, well, even though custom relays give us all these cool weird features, The basic Nostr feature of being able to follow anyone you want and not giving a super-peer the power to break that link between follower and followed, i.e. the outbox model, is still the most basic function of relays.
-
 @ 9e69e420:d12360c2
2025-02-01 11:16:04
@ 9e69e420:d12360c2
2025-02-01 11:16:04Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.

CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language.
One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse.
-
 @ 0fa80bd3:ea7325de
2025-01-29 05:55:02
@ 0fa80bd3:ea7325de
2025-01-29 05:55:02The land that belongs to the indigenous peoples of Russia has been seized by a gang of killers who have unleashed a war of extermination. They wipe out anyone who refuses to conform to their rules. Those who disagree and stay behind are tortured and killed in prisons and labor camps. Those who flee lose their homeland, dissolve into foreign cultures, and fade away. And those who stand up to protect their people are attacked by the misled and deceived. The deceived die for the unchecked greed of a single dictator—thousands from both sides, people who just wanted to live, raise their kids, and build a future.
Now, they are forced to make an impossible choice: abandon their homeland or die. Some perish on the battlefield, others lose themselves in exile, stripped of their identity, scattered in a world that isn’t theirs.
There’s been endless debate about how to fix this, how to clear the field of the weeds that choke out every new sprout, every attempt at change. But the real problem? We can’t play by their rules. We can’t speak their language or use their weapons. We stand for humanity, and no matter how righteous our cause, we will not multiply suffering. Victory doesn’t come from matching the enemy—it comes from staying ahead, from using tools they haven’t mastered yet. That’s how wars are won.
Our only resource is the will of the people to rewrite the order of things. Historian Timothy Snyder once said that a nation cannot exist without a city. A city is where the most active part of a nation thrives. But the cities are occupied. The streets are watched. Gatherings are impossible. They control the money. They control the mail. They control the media. And any dissent is crushed before it can take root.
So I started asking myself: How do we stop this fragmentation? How do we create a space where people can rebuild their connections when they’re ready? How do we build a self-sustaining network, where everyone contributes and benefits proportionally, while keeping their freedom to leave intact? And more importantly—how do we make it spread, even in occupied territory?
In 2009, something historic happened: the internet got its own money. Thanks to Satoshi Nakamoto, the world took a massive leap forward. Bitcoin and decentralized ledgers shattered the idea that money must be controlled by the state. Now, to move or store value, all you need is an address and a key. A tiny string of text, easy to carry, impossible to seize.
That was the year money broke free. The state lost its grip. Its biggest weapon—physical currency—became irrelevant. Money became purely digital.
The internet was already a sanctuary for information, a place where people could connect and organize. But with Bitcoin, it evolved. Now, value itself could flow freely, beyond the reach of authorities.
Think about it: when seedlings are grown in controlled environments before being planted outside, they get stronger, survive longer, and bear fruit faster. That’s how we handle crops in harsh climates—nurture them until they’re ready for the wild.
Now, picture the internet as that controlled environment for ideas. Bitcoin? It’s the fertile soil that lets them grow. A testing ground for new models of interaction, where concepts can take root before they move into the real world. If nation-states are a battlefield, locked in a brutal war for territory, the internet is boundless. It can absorb any number of ideas, any number of people, and it doesn’t run out of space.
But for this ecosystem to thrive, people need safe ways to communicate, to share ideas, to build something real—without surveillance, without censorship, without the constant fear of being erased.
This is where Nostr comes in.
Nostr—"Notes and Other Stuff Transmitted by Relays"—is more than just a messaging protocol. It’s a new kind of city. One that no dictator can seize, no corporation can own, no government can shut down.
It’s built on decentralization, encryption, and individual control. Messages don’t pass through central servers—they are relayed through independent nodes, and users choose which ones to trust. There’s no master switch to shut it all down. Every person owns their identity, their data, their connections. And no one—no state, no tech giant, no algorithm—can silence them.
In a world where cities fall and governments fail, Nostr is a city that cannot be occupied. A place for ideas, for networks, for freedom. A city that grows stronger the more people build within it.
-
 @ 57d1a264:69f1fee1
2024-08-12 15:35:34
@ 57d1a264:69f1fee1
2024-08-12 15:35:34Zap this meme for today (Special Edition) Meme Monday contest
originally posted at https://stacker.news/items/645698
-
 @ 3bf0c63f:aefa459d
2025-02-22 15:07:57
@ 3bf0c63f:aefa459d
2025-02-22 15:07:57document.characterSetand another meaningless example of flexibility destroying protocolsI always knew of at least two standardized ways browsers used to determine the charset of a given webpage document: the
Content-Typeheader and the<meta charset>tag. These are widely understood, teached and documented specs that a lot of developers assume are being followed because they're "web standards".Turns out there are a lot of pages on the internet that declare themselves as UTF-8 but are actually using other types of encoding (here's an example), and just by looking at the headers and meta tags you would think they are actually UTF-8, since they render correctly on Chromium and Firefox.
But the actual truth is that browsers actually ignore these headers completely and use their own internal heuristics to determine the actual charset. And they expose their internal result in the DOM property
document.characterSet."Oh, that's great! Technology is awesome, they've fixed a problem!", you may think. But the actual result of that is:
- developers never learn that they're wrongly declaring "UTF-8" when their content is actually "windows-1252" because they never see their page being rendered wrongly;
- the actual spec is now that browsers should correctly guess a page encoding instead of just following what is written;
- people are fooled and continue to teach, learn (and write) the falsehood of these useless HTTP headers and
<meta>tags not knowing they are completely wrong. - new browsers coming to the space have to first learn that this is a thing, which is not obvious nor written anywhere, then they must implement it, because if they follow the spec people will think it is their fault that some broken pages are rendered with broken characters on this new browser;
- barriers to entry are higher, the protocol continues to centralize more and more;
- other people trying to read these HTML pages for whatever reason, from any software that isn't Google Chrome or Mozilla Firefox, will have the same problem and will have to learn everything and come up with their own charset detection mechanism, this again closes the content of webpages to being more and more restricted to the walled garden of existing browser vendors.
I think we can all agree these are not good outcomes.
In the end of things, this is just a very small example, but "the web" protocol has thousands of such small examples, and they add up.
Also, arguably the spec should have been "browsers must do their own charset detection" since the beginning, but that's irrelevant. The fact is that it wasn't (and still isn't, the specs weren't updated as far as I know), and here's again another undeniable example of how being flexible can bloat a protocol.
-
 @ 0971cd37:53c969f4
2025-05-18 11:32:23
@ 0971cd37:53c969f4
2025-05-18 11:32:23ขุด Bitcoin หรือ Mining Bitcoin นั้นไม่ใช่เรื่องใหม่ แต่ในปัจจุบันการทำเหมืองขุดจากที่บ้าน(Home Miner)กลับมาได้รับความสนใจอีกครั้ง หลายๆคนกำลังหาเทคนิคให้คุ้มค่าและมีประสิทธิภาพสำหรับ Home Miner ที่ช่วยให้การขุดมีประสิทธิภาพมากขึ้นในบทความนี้
ก่อนเริ่มทำเหมืองขุดแบบ(Home Miner)ต้องนึกถึงสำรวจคิดทบทวนตัวเองว่าให้แน่ชัดเจน เป้าหมายเหมืองขุดBitcoin
- ทำเหมืองเพื่อสะสมออม Bitcoin โดยการใช้เครื่องขุด Bitcoin (ASIC)?
- ทำเพื่อเอา Bitcoin ขายเพื่อได้เงิน Fiat ใช้ และให้เป็นรายได้หลัก?
- เป็นผู้สร้างผลิตพลังงานใช้เองและเหลือพลังงานจากการผลิตเหมาะสมมั้ยที่จะทำเหมือง?
ทำเหมืองเพื่อสะสมออม Bitcoin โดยการใช้เครื่องขุด Bitcoin (ASIC)? ถ้าในกรณีทำเพื่อสะสมออม Bitcoin โดยการใช้เครื่องขุด ASIC (Application-Specific Integrated Circuit) นั้นถือเป็นวิธีที่เหมาะสมและมีประสิทธิภาพที่สุด เนื่องจาก ASIC ถูกออกแบบมาเฉพาะสำหรับการขุด Bitcoin โดยเฉพาะ ทำให้มีอัตราการขุด (Hashrate) ที่สูงและใช้พลังงานต่ำ
ข้อดี - Hashrate สูง สามารถขุด Bitcoin ได้รวดเร็วและมีโอกาสได้รับ Reward block Subsidy + fees มากขึ้น - ประหยัดพลังงาน ASIC ใช้พลังงานต่อ Hashrate ต่ำกว่า ในกรณีทำการ Tuning ASIC หรือ Low Power - ไม่จำเป็นต้องซื้อ Bitcoin ใน Exchange ไม่ต้อง KYC ไม่ต้องหาจังหวะการเข้าซื้อ Bitcoin ความผันผวนของราคาบน Exchange
ข้อเสีย
- ราคาสูง: ต้นทุนในการซื้อ ASIC ค่อนข้างสูง
ทำเหมืองเพื่อสร้างรายได้หลักจากการขาย Bitcoin? ถ้าในกรณีการทำเหมือง Bitcoin มองเป็นแหล่งรายได้หลักแต่ต้องบริหารมีการจัดการที่ดีด้วยเช่นกัน
ข้อดี - สร้างรายได้ประจำ หากสามารถคำนวณต้นทุนและรายได้ได้ดี จะสามารถขาย Bitcoin เป็นรายได้หลัก - มีสภาพคล่องสูง Bitcoin สามารถแลกเป็นเงินสด (Fiat) ได้อย่างรวดเร็วใน Exchange - ขยายระบบได้ง่าย สามารถเพิ่มเครื่องขุดเพื่อขยายกำลังการผลิต Hashrate เท่าที่จำเป็นความเหมาะสม สำหรับ Home Miner
ข้อเสีย
- ความผันผวนของราคา: ราคา Bitcoin มีการเปลี่ยนแปลงตลอดเวลา ทำให้ไม่สามารถคาดการณ์รายได้ได้แน่นอน
- การแข่งขันสูง จำนวนผู้ขุดมากขึ้นทำให้ Difficulty เพิ่มขึ้นเรื่อย ๆ
- ต้นทุนค่าไฟและค่าดูแล หากไม่จัดการพลังงานให้ดี ต้นทุนอาจสูงจนไม่คุ้มค่า
เป็นผู้สร้างผลิตพลังงานใช้เองและเหลือพลังงานจากการผลิตเหมาะสมมั้ยที่จะทำเหมือง? หากสามารถผลิตพลังงานไฟฟ้าใช้เองจากแหล่งพลังงานสะอาด เช่น โซล่าเซลล์ ความเหมาะสมการนำ พลังงานที่ผลิตได้มีเหลือใช้และไม่มีค่าเสียโอกาส การทำเหมืองขุด Bitcoin เล็กๆแบบ Home Miner ลดต้นทุนค่าไฟ,เพิ่มรายได้จากพลังงานส่วนเกิน, ลดระยะเวลาการคืนทุน ถือว่าคุ้มค่าที่จะทำ
จัดการพลังงานและค่าไฟฟ้า สำหรับ Home Miner หนึ่งในปัจจัยหลักของการขุดจากที่บ้านคือ ค่าไฟฟ้า ซึ่งสามารถลดลงได้ด้วยการ - มีโซล่าเซลล์ การใช้พลังงานแสงอาทิตย์เพื่อลดค่าไฟในช่วงกลางวัน - เลือกใช้มิเตอร์ TOU เลือกช่วงเวลาขุดการขุดในช่วง Off-Peak ที่ค่าไฟต่ำกว่าช่วง On-Peak - ทำการ Tuning ASIC เน้น Low Power
สรุปโดยรวม Home Miner เป็นวิธีหนึ่งการขุด Bitcoin ที่สามารถทำได้จากที่บ้าน หากมีการจัดการอุปกรณ์และพลังงานอย่างเหมาะสม รวมถึงการวางแผนการขุดในช่วงเวลาที่ค่าไฟฟ้าต่ำ และ การผลิตพลังงานเองจากโซล่าเซลล์ยังสามารถเพิ่มโอกาสในการลดต้นทุนและเพิ่มกำไรได้อีกด้วย
-
 @ 9e69e420:d12360c2
2025-02-17 17:12:01
@ 9e69e420:d12360c2
2025-02-17 17:12:01President Trump has intensified immigration enforcement, likening it to a wartime effort. Despite pouring resources into the U.S. Immigration and Customs Enforcement (ICE), arrest numbers are declining and falling short of goals. ICE fell from about 800 daily arrests in late January to fewer than 600 in early February.
Critics argue the administration is merely showcasing efforts with ineffectiveness, while Trump seeks billions more in funding to support his deportation agenda. Increased involvement from various federal agencies is intended to assist ICE, but many lack specific immigration training.
Challenges persist, as fewer immigrants are available for quick deportation due to a decline in illegal crossings. Local sheriffs are also pressured by rising demands to accommodate immigrants, which may strain resources further.
-
 @ 6be5cc06:5259daf0
2025-01-21 20:58:37
@ 6be5cc06:5259daf0
2025-01-21 20:58:37A seguir, veja como instalar e configurar o Privoxy no Pop!_OS.
1. Instalar o Tor e o Privoxy
Abra o terminal e execute:
bash sudo apt update sudo apt install tor privoxyExplicação:
- Tor: Roteia o tráfego pela rede Tor.
- Privoxy: Proxy avançado que intermedia a conexão entre aplicativos e o Tor.
2. Configurar o Privoxy
Abra o arquivo de configuração do Privoxy:
bash sudo nano /etc/privoxy/configNavegue até a última linha (atalho:
Ctrl+/depoisCtrl+Vpara navegar diretamente até a última linha) e insira:bash forward-socks5 / 127.0.0.1:9050 .Isso faz com que o Privoxy envie todo o tráfego para o Tor através da porta 9050.
Salve (
CTRL+OeEnter) e feche (CTRL+X) o arquivo.
3. Iniciar o Tor e o Privoxy
Agora, inicie e habilite os serviços:
bash sudo systemctl start tor sudo systemctl start privoxy sudo systemctl enable tor sudo systemctl enable privoxyExplicação:
- start: Inicia os serviços.
- enable: Faz com que iniciem automaticamente ao ligar o PC.
4. Configurar o Navegador Firefox
Para usar a rede Tor com o Firefox:
- Abra o Firefox.
- Acesse Configurações → Configurar conexão.
- Selecione Configuração manual de proxy.
- Configure assim:
- Proxy HTTP:
127.0.0.1 - Porta:
8118(porta padrão do Privoxy) - Domínio SOCKS (v5):
127.0.0.1 - Porta:
9050
- Proxy HTTP:
- Marque a opção "Usar este proxy também em HTTPS".
- Clique em OK.
5. Verificar a Conexão com o Tor
Abra o navegador e acesse:
text https://check.torproject.org/Se aparecer a mensagem "Congratulations. This browser is configured to use Tor.", a configuração está correta.
Dicas Extras
- Privoxy pode ser ajustado para bloquear anúncios e rastreadores.
- Outros aplicativos também podem ser configurados para usar o Privoxy.
-
 @ c9badfea:610f861a
2025-05-24 12:55:17
@ c9badfea:610f861a
2025-05-24 12:55:17Before you post a message or article online, let the LLM check if you are leaking any personal information using this prompt:
Analyze the following text to identify any Personally Identifiable Information (PII): <Your Message>Replace
<Your Message>with your textIf no PII is found, continue by modifying your message to detach it from your personality. You can use any of the following prompts (and further modify it if necessary).
Prompt № 1 - Reddit-Style
Convert the message into a casual, Reddit-style post without losing meaning. Split the message into shorter statements with the same overall meaning. Here is the message: <Your Message>Prompt № 2 - Advanced Modifications
``` Apply the following modifications to the message: - Rewrite it in lowercase - Use "u" instead of "you" - Use "akchoaly" instead of "actually" - Use "hav" instead of "have" - Use "tgat" instead of "that" - Use comma instead of period - Use British English grammar
Here is the message:
``` Prompt № 3 - Neutral Tone
Rewrite the message to correct grammar errors, and ensure the tone is neutral and free of emotional language: <Your Message>Prompt № 4 - Cross Translation Technique
Translate the message into Chinese, then translate the resulting Chinese text back into English. Provide only the final English translation. Here is the message: <Your Message>Check the modified message and send it.
ℹ️ You can use dialects to obfuscate your language further. For example, if you are from the US, you can tell the LLM to use British grammar and vice versa.
⚠️ Always verify the results. Don't fully trust an LLM.
-
 @ 8f69ac99:4f92f5fd
2025-02-20 15:24:24
@ 8f69ac99:4f92f5fd
2025-02-20 15:24:24Anarquia: uma palavra que frequentemente evoca imagens de caos e desordem, associada ao velho oeste sem lei ou a futuros distópicos onde impera a força bruta. No entanto, para aqueles que investigam mais a fundo, a anarquia revela-se como algo muito mais sofisticado—um sistema não definido pela ausência de regras, mas sim pela ausência de governantes (rules without rulers). Essa distinção fundamental é essencial para compreender um dos conceitos mais fascinantes e, ao mesmo tempo, mais difamados da sociedade.
A ideia de que anarquia significa desordem ou uma sociedade sem estrutura é um equívoco baseado no medo do desconhecido e na falta de compreensão dos seus princípios básicos. Na realidade, a anarquia assenta sobre um princípio fundamental: o Princípio da Não-Agressão (PNA). Este princípio estabelece que nenhum indivíduo tem o direito de iniciar o uso da força, coerção ou fraude contra os outros, sem o seu consentimento, sendo este um dos pilares fundamentais para a preservação da propriedade privada e das liberdades individuais.
Não se trata, portanto, de uma sociedade sem regras, mas sim de uma organização baseada em estruturas legais descentralizadas e orgânicas, como a lei natural e o direito consuetudinário, que emergem naturalmente através das interacções voluntárias entre indivíduos. A história demonstra que, mesmo na ausência de uma autoridade central, os seres humanos são perfeitamente capazes de criar ordens sociais complexas, baseadas na cooperação, na ajuda mútua e no progresso.
Este artigo explora como a anarquia funciona enquanto sistema de cooperação voluntária e direito natural, desafiando as concepções erradas que persistem sobre o tema e revelando o seu potencial para fortalecer a liberdade individual e a coesão social. Ao analisar as suas raízes filosóficas, o papel do Estado dentro de um enquadramento anarquista e os exemplos históricos que demonstram a capacidade da humanidade para se auto-organizar, procuramos iluminar um futuro onde a liberdade não seja apenas um sonho utópico, mas uma possibilidade concreta.
Principio da Não Agressão (PNA)
A base da anarquia assenta sobre um princípio inegociável: o Princípio da Não-Agressão. Este postulado não é apenas uma directriz moral, mas sim uma regra essencial de conduta, destinada a fomentar uma sociedade cooperativa e pacífica, onde os indivíduos vivem sem medo da coerção ou da violência.
A partir deste princípio, deriva-se naturalmente a propriedade privada, pois cada indivíduo tem o direito de usufruir e gerir os recursos que adquire sem recorrer à força contra terceiros. Da mesma forma, a violação deste princípio—seja através do roubo, homicídio ou qualquer tipo de agressão física ou psicológica, não consentida—é condenada de forma universal, pois representa um atentado contra a liberdade de cada um.
Num enquadramento anarquista, a ausência de uma estrutura coerciva não significa a ausência de ordem. Métodos como pressão social, ostracismo de infractores e mecanismos privados de justiça ajudam a manter a harmonia social. Por exemplo, em situações de litígio entre vizinhos sobre a posse de um terreno, em vez de recorrer ao Estado, poderiam simplesmente resolver a disputa através de um mediador comunitário ou de um serviço de arbitragem voluntário.
Ordem Sem Autoridade Central
A crença de que a lei e a ordem dependem de um poder centralizado ignora uma vasta tradição histórica de sistemas legais descentralizados que surgiram espontaneamente, sem intervenção estatal. A anarquia não significa ausência de normas, mas sim uma ordem espontânea baseada em leis naturais e consuetudinárias.
A lei natural consiste em princípios universais, reconhecidos pela razão, que não dependem da autoridade estatal. Já o direito consuetudinário assenta na tradição e nos precedentes, evoluindo conforme as necessidades das comunidades. Um excelente exemplo histórico é o código jurídico medieval islandês "Grágás", que regulava litígios e contratos através de mediação voluntária.
Sistemas baseados na reputação também são eficazes. No passado, comerciantes que desrespeitassem contratos viam-se rapidamente excluídos do mercado. Hoje, soluções descentralizadas como a arbitragem privada demonstram que contratos podem ser cumpridos sem necessidade de coerção estatal.
Anarquia como Estado Natural da Cooperação Humana
A cooperação voluntária está no cerne da natureza humana. A ideia de que é necessária uma autoridade central para garantir harmonia social desconsidera as inúmeras instâncias de colaboração espontânea ao longo da história.
O funcionamento dos mercados ilustra perfeitamente a anarquia em acção. Sem um governo a ditar regras, indivíduos interagem livremente, criando riqueza e inovação. A busca pelo progresso científico também reflecte este princípio: Albert Einstein, Nikola Tesla, Henry Ford ou Thomas Edison não foram forçados pelo Estado a desenvolver as suas invenções—fizeram-no por interesse próprio, beneficiando toda a humanidade.
Da mesma forma, a revolução industrial não foi um plano centralizado, mas sim o resultado de inúmeras inovações individuais que impulsionaram a prosperidade global. A tecnologia moderna, com exemplos como Bitcoin e Nostr, redes descentralizadas, prova que sociedades podem operar sem intermediários estatais, ou autoridades centrais.
Estado: Pode Existir Num Enquadramento Anarquista?
O Estado, mesmo na sua versão mais reduzida, pode representar um risco para a liberdade individual. Alguns, eu incluído, argumentam que um "Estado mínimo" (minarquia) poderia existir para garantir segurança e mediar disputas, mas essa estrutura pode rapidamente expandir-se e transformar-se num mecanismo de coerção.
A necessidade de mecanismos de controlo e equilíbrio
Mesmo um Estado reduzido exigiria salvaguardas para evitar abusos de poder. Para isso, seriam necessários mecanismos que garantam que nenhuma autoridade se torne dominante e que a sociedade mantenha a sua autonomia.
Algumas soluções incluem:
- Representação directa: Em vez de delegar decisões a políticos, a população poderia ter mais influência directa nas questões que afectam a sua vida (como na Suiça por exemplo).
- Arbitragem independente: Conflitos poderiam ser resolvidos sem recorrer a tribunais estatais, através de mediação voluntária e sistemas de justiça comunitária.
- Redes de apoio social: Fortalecer redes de ajuda mútua reduziria a necessidade de um governo central para fornecer serviços essenciais.
Exemplos práticos
Algumas iniciativas mostram que a sociedade pode funcionar com estruturas descentralizadas:
- Cidades com participação cívica activa: Experiências como o orçamento participativo em algumas cidades demonstram como a sociedade pode gerir recursos colectivos sem excessiva intervenção estatal.
- Redes de ajuda mútua: Grupos como a Mutual Aid Disaster Response Network nos EUA provam que comunidades podem organizar-se para responder a crises sem depender do Estado.
O desafio não é apenas imaginar um mundo sem Estado, mas conceber modelos descentralizados que garantam a liberdade individual e impeçam a concentração de poder. A verdadeira questão é: conseguiremos criar sistemas mais justos e funcionais sem recorrer à coerção estatal?
Raízes Filosóficas da Anarquia
A anarquia tem uma longa tradição filosófica que remonta a pensadores como William Godwin, Pierre-Joseph Proudhon e Max Stirner, cada um contribuindo com diferentes perspectivas sobre a organização social sem governantes. No século XX, pensadores como Murray Rothbard e Hans-Hermann Hoppe aprofundaram a ideia do anarco-capitalismo, propondo que todos os serviços actualmente providenciados pelo Estado poderiam ser oferecidos por meio de mercados livres.
A raiz histórica da anarquia está firmemente ancorada no pensamento de esquerda (a tradicional... ), na medida em que a sua proposta fundamental é a eliminação do poder central. O anarquismo clássico emergiu como uma resposta ao absolutismo e ao capitalismo industrial, defendendo que a autoridade imposta pelo Estado e pelas elites económicas deveria ser desmantelada para dar lugar a um sistema de cooperação voluntária e descentralizada. Proudhon, ao afirmar "a propriedade é roubo", reflectia esta preocupação com a concentração de poder e riqueza nas mãos de poucos.
Com o tempo, no entanto, diferentes correntes começaram a emergir dentro da tradição anarquista. A tradição anarquista de esquerda enfatiza a justiça social e a solidariedade comunitária, rejeitando tanto o Estado como o capitalismo. Nomes como Bakunin e Kropotkin defenderam a abolição da propriedade privada em favor de sistemas cooperativos, argumentando que apenas a auto gestão e o apoio mútuo poderiam garantir a verdadeira liberdade.
Por outro lado, no século XX, surgiu uma vertente anarquista mais associada à direita, especialmente com Rothbard e Hoppe, que viam o mercado como a melhor alternativa ao Estado. Para os anarco-capitalistas, a liberdade individual é prioritária, e a descentralização deve ocorrer não apenas ao nível político, mas também económico, permitindo que todas as transacções sejam voluntárias e baseadas na propriedade privada.
Apesar dessas divergências, há um ponto comum entre todas as vertentes anarquistas: a rejeição do monopólio da violência estatal. Tanto anarquistas de esquerda quanto de direita reconhecem que o poder centralizado inevitavelmente conduz à opressão e à limitação da liberdade individual. O debate interno dentro do anarquismo não é sobre a necessidade de abolir o Estado, mas sim sobre o que deve substituí-lo: auto gestão comunitária e colectivismo ou mercados livres e concorrência voluntária?
A preservação da propriedade privada e a liberdade de associação são, para mim, princípios fundamentais dentro do pensamento anarquista. Nada impede que, numa sociedade anarquista, grupos de indivíduos escolham unir-se voluntariamente para formar projectos cooperativos baseados em valores partilhados. O que distingue essa abordagem da imposição estatal é o carácter voluntário e descentralizado dessas associações, garantindo que cada pessoa possa viver conforme os seus próprios princípios sem coerção externa.
Esta dicotomia entre esquerda e direita dentro do anarquismo reflecte diferentes interpretações sobre a melhor forma de organizar a sociedade sem coerção. O que permanece inegável é que a anarquia, independentemente da vertente, continua a ser uma proposta de resistência contra qualquer forma de domínio centralizado, colocando a liberdade e a autonomia no centro da organização social.
Conclusão
A anarquia não é um sonho utópico, mas sim uma alternativa viável à organização centralizada da sociedade. Através do respeito pelo Princípio da Não-Agressão, da descentralização das normas jurídicas e da cooperação voluntária, podemos construir um mundo mais livre, onde as pessoas têm o poder de se governar a si mesmas.
Sistemas como Bitcoin já demonstram que a descentralização funciona e que a ausência de intermediários coercivos é não só possível, mas desejável. O desafio não é saber se a anarquia pode funcionar, mas sim quanto tempo levará para as pessoas perceberem que um mundo sem Estado é mais próspero e justo.
anarquia #anarco #bitcoin
Photo by Orit Matee on Unsplash
-
 @ 90c656ff:9383fd4e
2025-05-24 12:11:01
@ 90c656ff:9383fd4e
2025-05-24 12:11:01Since its creation, Bitcoin has marked a turning point in the digital money revolution—but its evolution didn’t stop at the original concept of decentralized transactions. Over the years, new technological solutions have been developed to expand its capabilities, making it more efficient and versatile. Among these innovations, smart contracts and the Lightning Network stand out, enabling increased functionality and scalability of the network, and ensuring a faster, cheaper, and more accessible system.
Smart contracts on Bitcoin
Smart contracts are programs that automatically execute certain actions when predefined conditions are met. Although the concept is more commonly associated with other networks, Bitcoin also supports smart contracts, especially through upgrades like Taproot.
- Smart contracts on Bitcoin enable functionalities such as:
01 - Conditional payments: Transactions that are only completed if certain rules are met, such as multi-signatures or specific time conditions.
02 - Advanced fund management: Use of multi-signature wallets, where different parties must approve a transaction before it is processed.
03 - Enhanced privacy: With the Taproot upgrade, smart contracts can be more efficient and indistinguishable from regular transactions, improving privacy across the network.
Although smart contracts on Bitcoin are simpler than those on other platforms, this simplicity is a strength—it preserves the network's security and robustness by avoiding complex vulnerabilities.
Lightning Network: scalability and instant transactions
One of the biggest challenges Bitcoin faces is scalability. Since the original network was designed to prioritize security and decentralization, transaction speed can be limited during periods of high demand. To address this issue, the Lightning Network was created—a second-layer solution that enables near-instant transactions with extremely low fees.
The Lightning Network works by creating payment channels between users, allowing them to conduct multiple transactions off-chain and recording only the final balance on the main Bitcoin blockchain or timechain. Key advantages include:
01 - Speed: Transactions are completed in milliseconds, making Bitcoin more suitable for daily payments.
02 - Low fees: Since transactions occur off-chain, fees are minimal, allowing for viable microtransactions.
03 - Network decongestion: By moving many transactions to the Lightning Network, Bitcoin’s main chain becomes more efficient and less congested.
In summary, Bitcoin continues to evolve technologically to meet the demands of a global financial system. Smart contracts increase its functionality, offering greater flexibility and security in transactions. The Lightning Network improves scalability, making Bitcoin faster and more practical for everyday use. With these innovations, Bitcoin remains at the forefront of the financial revolution, proving that despite its initial limitations, it continues to adapt and grow as a truly decentralized and global monetary system.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ 502ab02a:a2860397
2025-05-17 03:21:54
@ 502ab02a:a2860397
2025-05-17 03:21:54ยังมีเรื่องราวของน้ำตาล และ เซลล์ มาคุยกันต่อนะครับ เพราะยังมีคนสงสัยอยู่ว่า เอ้ย ตกลงต้องห่วงการ Spike&Staylong ของอินซุลินอยู่หรือเปล่า แล้วถ้าเราไม่ spike&staylong ก็คือกินคาร์บเบาๆตลอดวันได้เลยใช่ไหมก็มันไม่ spike&staylong แล้วนี่ โอเคครับ เรามาเปิดผับกันอีกครั้ง
คราวก่อนนั้นเราคุยกันเรื่อง ผับน้ำตาลกันไปแล้วนะครับว่า เมื่ออินซูลิน spike สูง และค้างนาน เหมือนเปิดผับแล้ววัยรุ่นแห่กันเข้ามาเที่ยว จนพีอาร์เมาจัด
เผื่อใครจำไม่ได้ ย้อนให้นิดๆครับ ว่าให้ลองนึกภาพว่าเฮียเปิดผับอยู่ดี ๆ ลูกค้าหลั่งไหลเข้ามารัว ๆ เหมือนมีโปรเบียร์ 1 แถม 10 ตอนสามทุ่ม ทุกโต๊ะสั่งข้าวเหนียวหมูปิ้งพร้อมเบียร์น้ำแข็งเต็มโต๊ะ นักเที่ยวก็ยังแห่เข้าผับแบบไม่มีพัก อินซูลินซึ่งเป็นเหมือน “พีอาร์” ที่ต้องจัดการรับแขก (หรือรับน้ำตาลเข้าสู่เซลล์) ก็เลยต้องทำงานหนักแบบ non-stop
อินซูลินเป็นฮอร์โมนสำคัญที่ช่วยเอาน้ำตาลในเลือดเข้าไปเก็บในเซลล์ ถ้า spike ทีเดียวสูงมาก เซลล์ก็รีบดูดน้ำตาลเข้าไปเต็มที่จนเกินพิกัด เหมือนผับที่แน่นจนปิดประตูไม่ลง
ถ้าเหตุการณ์แบบนี้เกิดขึ้นบ่อย ๆ ร่างกายจะเริ่มรู้สึกว่า “ทำไมอินซูลินถึงต้องออกมาบ่อยขนาดนี้วะ?” ระบบก็เริ่มปิดรับแขก เซลล์เริ่มไม่อยากตอบสนอง เพราะมันเหนื่อย มันชิน และมันก็เริ่ม “ดื้ออินซูลิน”
ผลที่ตามมาเมื่อ spike สูงและค้าง สิ่งที่ตามมา... คือความปั่นป่วนในร่างกายอย่างต่อเนื่อง น้ำตาลลอยค้างในเลือด ไปจับกับโปรตีนจนกลายเป็นเจ้า AGEs ตัวร้าย ไขมันก็ถูกสร้างมากขึ้น ล้นเข้าไปสะสมในตับ ในพุง ในซอกที่ร่างกายไม่รู้จะเก็บไว้ตรงไหนแล้ว สมองก็เบลอ ใจวูบ ง่วงงุน... เหมือนเข้าเวรประชุมยาวแบบไม่มีกาแฟ ฮอร์โมนที่เคยเป็นทีมงานสามัคคี ก็เริ่มทะเลาะกันเอง อินซูลินงอน leptin งง ghrelin งวย
แล้วถ้าเราไม่ spike แต่กินคาร์บจุ๋มจิ๋มทั้งวันล่ะ? พอรู้ว่าการเปิดผับแจกคาร์บแบบจัดหนักไม่ดี หลายคนก็ปรับกลยุทธ์ใหม่ มาแนวสายสุขุมว่า “งั้นเปิดผับแบบเนิบ ๆ ก็แล้วกัน… ไม่จัดปาร์ตี้ใหญ่ แต่มีแขกแวะเข้ามาทั้งวัน” ฟังดูดีใช่ไหม? แต่เอาเข้าจริง มันเหนื่อยไม่แพ้กันเลย
ลองนึกภาพว่าประเทศไม่มีเคอร์ฟิว เฮียเปิดผับที่มีลูกค้าเดินเข้าออกไม่หยุด ไม่ได้มากันเป็นฝูงแบบรอบโปรโมชั่น แต่มาเรื่อย ๆ แบบชั่วโมงละโต๊ะ สองโต๊ะ พีอาร์ อินซูลิน ก็เลยต้องยืนต้อนรับแขกตลอดเวลา ไม่มีเวลานั่งพัก ไม่มีช่วงเปลี่ยนกะ ไม่มีเวลาปิดไฟเก็บโต๊ะ คือทำงานต่อเนื่องยาว ๆ ตั้งแต่ 8 โมงเช้า ยัน 8 โมงเช้า สุดท้าย ผับก็เปิดไฟยันสว่าง อินซูลินก็กลายเป็นพนักงานกะดึกตลอดชีพ และเมื่อไม่มีเวลา “พักผับ” ระบบหลังบ้านก็ไม่เคยได้ฟื้นฟูเลย
ภาพรวมของการกินจุ๋มจิ๋มทั้งวันแบบนี้นั้น - เผาผลาญไขมันไม่ออกเลย เพราะอินซูลินทำหน้าที่เหมือนไฟบนเวที ถ้ายังเปิดไฟอยู่ “เครื่องดูดไขมันหลังร้าน” มันก็ไม่ทำงาน - แม่บ้านทำความสะอาดก็เข้าไม่ได้ เพราะแขกเดินเข้าเดินออกตลอด ระบบกำจัดที่ควรจะได้ล้างของเสียในเซลล์ ก็เลยโดนขัดจังหวะตลอด - พนักงานเหนื่อยสะสมจากงานไม่มีหยุด ทำให้เกิดความเครียดสะสมในร่างกาย ฮอร์โมนรวน อารมณ์ก็แปรปรวนง่ายขึ้น หิวเก่งขึ้น ทั้งที่เพิ่งกินไป
เปิดผับแบบคึกคักจัดเต็มทีเดียว แล้วปิดยาว หรือ เปิดทั้งวันแบบไม่มีช่วงปิด สุดท้ายพังทั้งคู่
ทีนี้เราน่าจะพอเห็นภาพร่างคร่าวๆ ของการบริหารการจัดการน้ำตาลในตัวเราได้แล้วนะครับ ว่าจะไดเอทไหนก็ตาม การบริหารการจัดการฮอร์โมนส์ คือสิ่งสำคัญไม่แพ้เรื่องอื่นๆ แม้จะไม่ใช่เรื่องสำคัญที่สุดในสายตาใครก็ตาม
นี่เป็นเพียงจุดเริ่มต้นการเรียนรู้เล็กๆ ซึ่งเส้นทางสายที่เรียกว่า ร่างกาย มันยังไปไกลอีกลิบลับเลยครับ ไม่ว่าจะจังหวัดคอติซอล จังหวัดพฤกษเคมี จังหวัดพลังงาน จังหวัดสารอาหาร แถมลักษณะร่างกายแต่ละคน ก็เปรียบเหมือนรถต่างยี่ห้อ ต่างน้ำมันขับเคลื่อน ต่างซีซี หรือแม้ว่าจะเหมือนกัน ก็ยังต่างปี ต่างไมล์การขับขี่
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ fd208ee8:0fd927c1
2025-02-15 07:02:08
@ fd208ee8:0fd927c1
2025-02-15 07:02:08E-cash are coupons or tokens for Bitcoin, or Bitcoin debt notes that the mint issues. The e-cash states, essentially, "IoU 2900 sats".
They're redeemable for Bitcoin on Lightning (hard money), and therefore can be used as cash (softer money), so long as the mint has a good reputation. That means that they're less fungible than Lightning because the e-cash from one mint can be more or less valuable than the e-cash from another. If a mint is buggy, offline, or disappears, then the e-cash is unreedemable.
It also means that e-cash is more anonymous than Lightning, and that the sender and receiver's wallets don't need to be online, to transact. Nutzaps now add the possibility of parking transactions one level farther out, on a relay. The same relays that cannot keep npub profiles and follow lists consistent will now do monetary transactions.
What we then have is * a transaction on a relay that triggers * a transaction on a mint that triggers * a transaction on Lightning that triggers * a transaction on Bitcoin.
Which means that every relay that stores the nuts is part of a wildcat banking system. Which is fine, but relay operators should consider whether they wish to carry the associated risks and liabilities. They should also be aware that they should implement the appropriate features in their relay, such as expiration tags (nuts rot after 2 weeks), and to make sure that only expired nuts are deleted.
There will be plenty of specialized relays for this, so don't feel pressured to join in, and research the topic carefully, for yourself.
https://github.com/nostr-protocol/nips/blob/master/60.md
-
 @ 97c70a44:ad98e322
2025-02-18 20:30:32
@ 97c70a44:ad98e322
2025-02-18 20:30:32For the last couple of weeks, I've been dealing with the fallout of upgrading a web application to Svelte 5. Complaints about framework churn and migration annoyances aside, I've run into some interesting issues with the migration. So far, I haven't seen many other people register the same issues, so I thought it might be constructive for me to articulate them myself.
I'll try not to complain too much in this post, since I'm grateful for the many years of Svelte 3/4 I've enjoyed. But I don't think I'll be choosing Svelte for any new projects going forward. I hope my reflections here will be useful to others as well.
If you're interested in reproductions for the issues I mention here, you can find them below.
The Need for Speed
To start with, let me just quickly acknowledge what the Svelte team is trying to do. It seems like most of the substantial changes in version 5 are built around "deep reactivity", which allows for more granular reactivity, leading to better performance. Performance is good, and the Svelte team has always excelled at reconciling performance with DX.
In previous versions of Svelte, the main way this was achieved was with the Svelte compiler. There were many ancillary techniques involved in improving performance, but having a framework compile step gave the Svelte team a lot of leeway for rearranging things under the hood without making developers learn new concepts. This is what made Svelte so original in the beginning.
At the same time, it resulted in an even more opaque framework than usual, making it harder for developers to debug more complex issues. To make matters worse, the compiler had bugs, resulting in errors which could only be fixed by blindly refactoring the problem component. This happened to me personally at least half a dozen times, and is what ultimately pushed me to migrate to Svelte 5.
Nevertheless, I always felt it was an acceptable trade-off for speed and productivity. Sure, sometimes I had to delete my project and port it to a fresh repository every so often, but the framework was truly a pleasure to use.
Svelte is not Javascript
Svelte 5 doubled down on this tradeoff — which makes sense, because it's what sets the framework apart. The difference this time is that the abstraction/performance tradeoff did not stay in compiler land, but intruded into runtime in two important ways:
- The use of proxies to support deep reactivity
- Implicit component lifecycle state
Both of these changes improved performance and made the API for developers look slicker. What's not to like? Unfortunately, both of these features are classic examples of a leaky abstraction, and ultimately make things more complex for developers, not less.
Proxies are not objects
The use of proxies seems to have allowed the Svelte team to squeeze a little more performance out of the framework, without asking developers to do any extra work. Threading state through multiple levels of components without provoking unnecessary re-renders in frameworks like React is an infamously difficult chore.
Svelte's compiler avoided some of the pitfalls associated with virtual DOM diffing solutions, but evidently there was still enough of a performance gain to be had to justify the introduction of proxies. The Svelte team also seems to argue that their introduction represents an improvement in developer experience:
we... can maximise both efficiency and ergonomics.
Here's the problem: Svelte 5 looks simpler, but actually introduces more abstractions.
Using proxies to monitor array methods (for example) is appealing because it allows developers to forget all the goofy heuristics involved with making sure state was reactive and just
pushto the array. I can't count how many times I've writtenvalue = valueto trigger reactivity in svelte 4.In Svelte 4, developers had to understand how the Svelte compiler worked. The compiler, being a leaky abstraction, forced its users to know that assignment was how you signaled reactivity. In svelte 5, developers can just "forget" about the compiler!
Except they can't. All the introduction of new abstractions really accomplishes is the introduction of more complex heuristics that developers have to keep in their heads in order to get the compiler to act the way they want it to.
In fact, this is why after years of using Svelte, I found myself using Svelte stores more and more often, and reactive declarations less. The reason being that Svelte stores are just javascript. Calling
updateon a store is simple, and being able to reference them with a$was just a nice bonus — nothing to remember, and if I mess up the compiler yells at me.Proxies introduce a similar problem to reactive declarations, which is that they look like one thing but act like another on the edges.
When I started using Svelte 5, everything worked great — until I tried to save a proxy to indexeddb, at which point I got a
DataCloneError. To make matters worse, it's impossible to reliably tell if something is aProxywithouttry/catching a structured clone, which is a performance-intensive operation.This forces the developer to remember what is and what isn't a Proxy, calling
$state.snapshotevery time they pass a proxy to a context that doesn't expect or know about them. This obviates all the nice abstractions they gave us in the first place.Components are not functions
The reason virtual DOM took off way back in 2013 was the ability to model your application as composed functions, each of which takes data and spits out HTML. Svelte retained this paradigm, using a compiler to sidestep the inefficiencies of virtual DOM and the complexities of lifecycle methods.
In Svelte 5, component lifecycles are back, react-hooks style.
In React, hooks are an abstraction that allows developers to avoid writing all the stateful code associated with component lifecycle methods. Modern React tutorials universally recommend using hooks instead, which rely on the framework invisibly synchronizing state with the render tree.
While this does result in cleaner code, it also requires developers to tread carefully to avoid breaking the assumptions surrounding hooks. Just try accessing state in a
setTimeoutand you'll see what I mean.Svelte 4 had a few gotchas like this — for example, async code that interacts with a component's DOM elements has to keep track of whether the component is unmounted. This is pretty similar to the kind of pattern you'd see in old React components that relied on lifecycle methods.
It seems to me that Svelte 5 has gone the React 16 route by adding implicit state related to component lifecycles in order to coordinate state changes and effects.
For example, here is an excerpt from the documentation for $effect:
You can place $effect anywhere, not just at the top level of a component, as long as it is called during component initialization (or while a parent effect is active). It is then tied to the lifecycle of the component (or parent effect) and will therefore destroy itself when the component unmounts (or the parent effect is destroyed).
That's very complex! In order to use
$effect... effectively (sorry), developers have to understand how state changes are tracked. The documentation for component lifecycles claims:In Svelte 5, the component lifecycle consists of only two parts: Its creation and its destruction. Everything in-between — when certain state is updated — is not related to the component as a whole; only the parts that need to react to the state change are notified. This is because under the hood the smallest unit of change is actually not a component, it’s the (render) effects that the component sets up upon component initialization. Consequently, there’s no such thing as a “before update”/"after update” hook.
But then goes on to introduce the idea of
tickin conjunction with$effect.pre. This section explains that "tickreturns a promise that resolves once any pending state changes have been applied, or in the next microtask if there are none."I'm sure there's some mental model that justifies this, but I don't think the claim that a component's lifecycle is only comprised of mount/unmount is really helpful when an addendum about state changes has to come right afterward.
The place where this really bit me, and which is the motivation for this blog post, is when state gets coupled to a component's lifecycle, even when the state is passed to another function that doesn't know anything about svelte.
In my application, I manage modal dialogs by storing the component I want to render alongside its props in a store and rendering it in the
layout.svelteof my application. This store is also synchronized with browser history so that the back button works to close them. Sometimes, it's useful to pass a callback to one of these modals, binding caller-specific functionality to the child component:javascript const {value} = $props() const callback = () => console.log(value) const openModal = () => pushModal(MyModal, {callback})This is a fundamental pattern in javascript. Passing a callback is just one of those things you do.
Unfortunately, if the above code lives in a modal dialog itself, the caller component gets unmounted before the callback gets called. In Svelte 4, this worked fine, but in Svelte 5
valuegets updated toundefinedwhen the component gets unmounted. Here's a minimal reproduction.This is only one example, but it seems clear to me that any prop that is closed over by a callback function that lives longer than its component will be undefined when I want to use it — with no reassignment existing in lexical scope. It seems that the reason this happens is that the props "belong" to the parent component, and are accessed via getters so that the parent can revoke access when it unmounts.
I don't know why this is necessary, but I assume there's a good engineering reason for it. The problem is, this just isn't how javascript works. Svelte is essentially attempting to re-invent garbage collection around component lifecycles, which breaks the assumption every javascript developer has that variables don't simply disappear without an explicit reassignment. It should be safe to pass stuff around and let the garbage collector do its job.
Conclusion
Easy things are nice, but as Rich Hickey says, easy things are not always simple. And like Joel Spolsky, I don't like being surprised. Svelte has always been full of magic, but with the latest release I think the cognitive overhead of reciting incantations has finally outweighed the power it confers.
My point in this post is not to dunk on the Svelte team. I know lots of people like Svelte 5 (and react hooks). The point I'm trying to make is that there is a tradeoff between doing things on the user's behalf, and giving the user agency. Good software is built on understanding, not cleverness.
I also think this is an important lesson to remember as AI-assisted coding becomes increasingly popular. Don't choose tools that alienate you from your work. Choose tools that leverage the wisdom you've already accumulated, and which help you to cultivate a deeper understanding of the discipline.
Thank you to Rich Harris and team for many years of pleasant development. I hope that (if you read this) it's not so full of inaccuracies as to be unhelpful as user feedback.
-
 @ 8cb60e21:5f2deaea
2024-08-09 15:31:52
@ 8cb60e21:5f2deaea
2024-08-09 15:31:52```js import NextAuth from "next-auth"; import CredentialsProvider from "next-auth/providers/credentials"; import NDK from "@nostr-dev-kit/ndk"; import axios from "axios"; import { findKind0Fields } from "@/utils/nostr";
const relayUrls = [ "wss://nos.lol/", "wss://relay.damus.io/", "wss://relay.snort.social/", "wss://relay.nostr.band/", "wss://nostr.mutinywallet.com/", "wss://relay.mutinywallet.com/", "wss://relay.primal.net/" ];
const BASE_URL = process.env.BASE_URL;
const ndk = new NDK({ explicitRelayUrls: relayUrls, });
export default NextAuth({ providers: [ CredentialsProvider({ id: "nostr", name: "Nostr", credentials: { pubkey: { label: "Public Key", type: "text" }, }, authorize: async (credentials) => { if (credentials?.pubkey) { await ndk.connect();
const user = ndk.getUser({ pubkey: credentials.pubkey }); try { const profile = await user.fetchProfile(); // Check if user exists, create if not const response = await axios.get(`${BASE_URL}/api/users/${credentials.pubkey}`); if (response.status === 200 && response.data) { const fields = await findKind0Fields(profile); // Combine user object with kind0Fields, giving priority to kind0Fields const combinedUser = { ...response.data, ...fields }; // Update the user on the backend if necessary // await axios.put(`${BASE_URL}/api/users/${combinedUser.id}`, combinedUser); return combinedUser; } else if (response.status === 204) { // Create user if (profile) { const fields = await findKind0Fields(profile); console.log('FEEEEELDS', fields); const payload = { pubkey: credentials.pubkey, ...fields }; const createUserResponse = await axios.post(`${BASE_URL}/api/users`, payload); return createUserResponse.data; } } } catch (error) { console.error("Nostr login error:", error); } } return null; }, }), ], callbacks: { async jwt({ token, user }) { // Add combined user object to the token if (user) { token.user = user; } return token; }, async session({ session, token }) { // Add user from token to session session.user = token.user; session.jwt = token; return session; }, async redirect({ url, baseUrl }) { return baseUrl; }, }, secret: process.env.NEXTAUTH_SECRET, session: { strategy: "jwt" }, jwt: { signingKey: process.env.JWT_SECRET, }, pages: { signIn: "/auth/signin", },}); ```
-
 @ 9e69e420:d12360c2
2025-01-21 19:31:48
@ 9e69e420:d12360c2
2025-01-21 19:31:48Oregano oil is a potent natural compound that offers numerous scientifically-supported health benefits.
Active Compounds
The oil's therapeutic properties stem from its key bioactive components: - Carvacrol and thymol (primary active compounds) - Polyphenols and other antioxidant
Antimicrobial Properties
Bacterial Protection The oil demonstrates powerful antibacterial effects, even against antibiotic-resistant strains like MRSA and other harmful bacteria. Studies show it effectively inactivates various pathogenic bacteria without developing resistance.
Antifungal Effects It effectively combats fungal infections, particularly Candida-related conditions like oral thrush, athlete's foot, and nail infections.
Digestive Health Benefits
Oregano oil supports digestive wellness by: - Promoting gastric juice secretion and enzyme production - Helping treat Small Intestinal Bacterial Overgrowth (SIBO) - Managing digestive discomfort, bloating, and IBS symptoms
Anti-inflammatory and Antioxidant Effects
The oil provides significant protective benefits through: - Powerful antioxidant activity that fights free radicals - Reduction of inflammatory markers in the body - Protection against oxidative stress-related conditions
Respiratory Support
It aids respiratory health by: - Loosening mucus and phlegm - Suppressing coughs and throat irritation - Supporting overall respiratory tract function
Additional Benefits
Skin Health - Improves conditions like psoriasis, acne, and eczema - Supports wound healing through antibacterial action - Provides anti-aging benefits through antioxidant properties
Cardiovascular Health Studies show oregano oil may help: - Reduce LDL (bad) cholesterol levels - Support overall heart health
Pain Management The oil demonstrates effectiveness in: - Reducing inflammation-related pain - Managing muscle discomfort - Providing topical pain relief
Safety Note
While oregano oil is generally safe, it's highly concentrated and should be properly diluted before use Consult a healthcare provider before starting supplementation, especially if taking other medications.
-
 @ 8cb60e21:5f2deaea
2024-08-09 14:57:34
@ 8cb60e21:5f2deaea
2024-08-09 14:57:34lorem ipsum
-
 @ 90c656ff:9383fd4e
2025-05-24 12:06:36
@ 90c656ff:9383fd4e
2025-05-24 12:06:36Throughout history, money has always been under the control of central authorities, such as governments and banks. These intermediaries have set the rules of the financial system, controlled the issuance of currency, and overseen transactions. However, with the emergence of Bitcoin, a new paradigm began to take shape: decentralized money. This transformation represents a profound shift in how people store and transfer value, challenging the traditional financial model.
- The traditional model: centralized money
01 - Dependence on intermediaries: To carry out transactions, people rely on banks, governments, and other regulatory entities.
02 - Inflation and devaluation: Central banks can print money endlessly, often leading to a loss in purchasing power.
03 - Censorship and restrictions: Access to money can be denied for political, bureaucratic, or institutional reasons, limiting individuals’ financial freedom.
Despite being the dominant model for centuries, the centralized system has shown its vulnerabilities through numerous economic and political crises. It was in this context that Bitcoin emerged as an innovative alternative.
- The revolution of decentralized money
01 - Elimination of intermediaries: Transactions can be made directly between users, without the need for banks or financial companies.
02 - Limited and predictable supply: Bitcoin has a fixed cap of 21 million units, preventing the inflation caused by excessive money printing.
03 - Censorship resistance: No entity can block or prevent transactions, ensuring full financial freedom.
04 - Self-custody: Each user can hold their own funds without relying on a bank or any other institution.
This paradigm shift has a significant impact not only on the financial system but also on how people interact with money and protect their wealth.
Challenges and opposition to financial decentralization
The transition to a decentralized financial system faces several challenges, the main one being resistance from traditional institutions. Banks and governments see Bitcoin as a threat to their control over money and seek to regulate or limit its adoption.
There are also technical and educational barriers. Many people still do not fully understand how Bitcoin works, which can hinder its adoption. However, as more people become aware of the benefits of decentralized money, its use is likely to grow.
In summary, the shift from a centralized financial system to a decentralized one represents one of the most significant transformations of the digital era. Bitcoin leads this movement by offering a censorship-resistant, transparent, and accessible alternative. Despite opposition from the traditional system, the decentralization of money continues to gain momentum, providing greater autonomy and financial freedom to people around the world. This revolution is not just technological, but also social and economic—redefining the way the world understands and uses money.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ 97c70a44:ad98e322
2025-02-17 14:29:00
@ 97c70a44:ad98e322
2025-02-17 14:29:00Everyone knows that relays are central to how nostr works - they're even in the name: Notes and Other Stuff Transmitted by Relays. As time goes on though, there are three other letters which are becoming conspicuously absent from our beloved and ambiguously pronounceable acronym - "D", "V", and "M".
For the uninitiated, DVM stands for "data vending machines". They're actually sort of hard to describe — in technical terms they act more like clients, since they simply read events from and publish events to relays. In most cases though, these events are part of a request/response flow initiated by users elsewhere on the network. In practice, DVMs are bots, but there's also nothing to prevent the work they do from being powered by human interaction. They're an amazingly flexible tool for building anything from custom feeds, to transcription services, to chatbots, to protocol gateways.
The hype cycle for DVMs seems to have reached escape velocity in a way few other things have - zaps being the possible exception. But what exactly DVMs are remains something of a mystery to many nostr developers - and how to build one may as well be written on clay tablets.
This blog post is designed to address that - below is a soup to nuts (no nutzaps though) guide to building a DVM flow, both from the client and the server side.
Here's what we'll be covering:
- Discovering DVM metadata
- Basic request/response flow
- Implementing a minimal example
Let's get started!
DVM Metadata
First of all, it's helpful to know how DVMs are reified on the nostr network. While not strictly necessary, this can be useful for discovering DVMs and presenting them to users, and for targeting specific DVMs we want a response from.
NIP 89 goes into this in more detail, but the basic idea is that anyone can create a
kind 31990"application handler" event and publish it to the network with their own (or a dedicated) public key. This handler was originally intended to advertise clients, but has been re-purposed for DVM listings as well.Here's what the "Fluffy Frens" handler looks like:
json { "content": "{\"name\": \"Fluffy Frens\", \"picture\": \"https://image.nostr.build/f609311532c470f663e129510a76c9a1912ae9bc4aaaf058e5ba21cfb512c88e.jpg\", \"about\": \"I show recent notes about animals\", \"lud16\": \"discovery_content_fluffy@nostrdvm.com\", \"supportsEncryption\": true, \"acceptsNutZaps\": false, \"personalized\": false, \"amount\": \"free\", \"nip90Params\": {\"max_results\": {\"required\": false, \"values\": [], \"description\": \"The number of maximum results to return (default currently 100)\"}}}", "created_at": 1738874694, "id": "0aa8d1f19cfe17e00ce55ca86fea487c83be39a1813601f56f869abdfa776b3c", "kind": 31990, "pubkey": "7b7373dd58554ff4c0d28b401b9eae114bd92e30d872ae843b9a217375d66f9d", "sig": "22403a7996147da607cf215994ab3b893176e5302a44a245e9c0d91214e4c56fae40d2239dce58ea724114591e8f95caed2ba1a231d09a6cd06c9f0980e1abd5", "tags": [ ["k", "5300"], ["d", "198650843898570c"] ] }This event is rendered in various clients using the kind-0-style metadata contained in the
contentfield, allowing users to browse DVMs and pick one for their use case. If a user likes using a particular DVM, they might publish akind 31989"application recommendation", which other users can use to find DVMs that are in use within their network.Note the
ktag in the handler event - this allows DVMs to advertise support only for specific job types. It's also important to note that even though the spec doesn't cover relay selection, most clients use the publisher'skind 10002event to find out where the DVM listens for events.If this looks messy to you, you're right. See this PR for a proposal to split DVMs out into their own handler kind, give them a dedicated pubkey along with dedicated metadata and relay selections, and clean up the data model a bit.
DVM Flow
Now that we know what a DVM looks like, we can start to address how they work. My explanation below will elide some of the detail involved in NIP 90 for simplicity, so I encourage you to read the complete spec.
The basic DVM flow can be a little (very) confusing to work with, because in essence it's a request/response paradigm, but it has some additional wrinkles.
First of all, the broker for the request isn't abstracted away as is usually the case with request/response flows. Regular HTTP requests involve all kinds of work in the background - from resolving domain names to traversing routers, VPNs, and ISP infrastructure. But developers don't generally have to care about all these intermediaries.
With DVMs, on the other hand, the essential complexity of relay selection can't simply be ignored. DVMs often advertise their own relay selections, which should be used rather than a hard-coded or randomly chosen relay to ensure messages are delivered. The benefit of this is that DVMs can avoid censorship, just as users can, by choosing relays that are willing to broker their activity. DVMs can even select multiple relays to broker requests, which means that clients might receive multiple copies of the same response.
Secondly, the DVM request/response model is far more fluid than is usually the case with request/response flows. There are a set of standard practices, but the flow is flexible enough to admit exceptions to these conventions for special use cases. Here are some examples:
- Normally, clients p-tag the DVM they wish to address. But if a client isn't picky about where a response comes from, they may choose to send an open request to the network and collect responses from multiple DVMs simultaneously.
- Normally, a client creates a request before collecting responses using a subscription with an e-tag filter matching the request event. But clients may choose to skip the request step entirely and collect responses from the network that have already been created. This can be useful for computationally intensive tasks or common queries, where a single result can be re-used multiple times.
- Sometimes, a DVM may respond with a
kind 7000job status event to let clients know they're working on the request. This is particularly useful for longer-running tasks, where feedback is useful for building a responsive UX. - There are also some details in the spec regarding monetization, parameterization, error codes, encryption, etc.
Example DVM implementation
For the purposes of this blog post, I'll keep things simple by illustrating the most common kind of DVM flow: a
kind 5300content discovery request, addressed to a particular DVM. If you're interested in other use cases, please visit data-vending-machines.org for additional documented kinds.The basic flow looks like this:
- The DVM starts by listening for
kind 5300job requests on some relays it has selected and advertised via NIP 89 (more on that later) - A client creates a request event of
kind 5300, p-tagged with the DVM's pubkey and sends it to the DVM's relay selections. - The DVM receives the event and processes it, issuing optional
kind 7000job status events, and eventually issuing akind 6300job result event (job result event kinds are always 1000 greater than the request's kind). - The client listens to the same relays for a response, and when it comes through does whatever it wants to with it.
Here's a swimlane diagram of that flow:
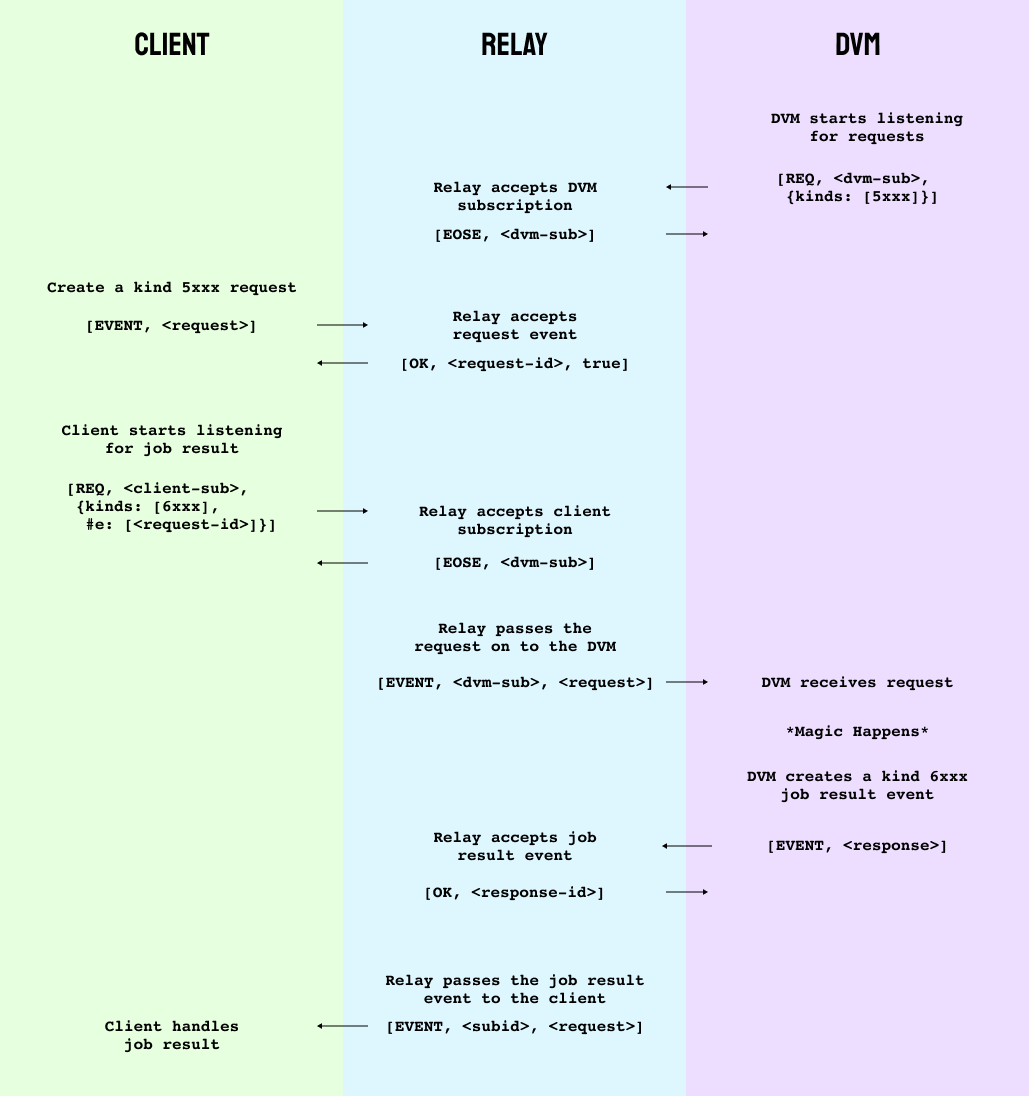
To avoid massive code samples, I'm going to implement our DVM entirely using nak (backed by the power of the human mind).
The first step is to start our DVM listening for requests that it wants to respond to. Nak's default pubkey is
79be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798, so we'll only listen for requests sent to nak.bash nak req -k 5300 -t p=79be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798This gives us the following filter:
json ["REQ","nak",{"kinds":[5300],"#p":["79be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798"]}]To open a subscription to
nos.loland stream job requests, add--stream wss://nos.lolto the previous request and leave it running.Next, open a new terminal window for our "client" and create a job request. In this case, there's nothing we need to provide as
input, but we'll include it just for illustration. It's also good practice to include anexpirationtag so we're not asking relays to keep our ephemeral requests forever.bash nak event -k 5300 -t p=79be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798 -t expiration=$(( $(date +%s) + 30 )) -t input=helloHere's what comes out:
json { "kind": 5300, "id": "0e419d0b3c5d29f86d2132a38ca29cdfb81a246e1a649cb2fe1b9ed6144ebe30", "pubkey": "79be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798", "created_at": 1739407684, "tags": [ ["p", "79be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798"], ["expiration", "1739407683"], ["input", "hello"] ], "content": "", "sig": "560807548a75779a7a68c0ea73c6f097583e2807f4bb286c39931e99a4e377c0a64af664fa90f43e01ddd1de2e9405acd4e268f1bf3bc66f0ed5a866ea093966" }Now go ahead and publish this event by adding
nos.lolto the end of yournakcommand. If all goes well, you should see your event pop up in your "dvm" subscription. If so, great! That's half of the flow.Next, we'll want our client to start listening for
kind 6300responses to the request. In your "client" terminal window, run:bash nak req -k 6300 -t e=<your-eventid-here> --stream nos.lolNote that if you only want to accept responses from the specified DVM (a good policy in general to avoid spam) you would include a
ptag here. I've omitted it for brevity. Also notice thektag specifies the request kind plus1000- this is just a convention for what kinds requests and responses use.Now, according to data-vending-machines.org,
kind 5300responses are supposed to put a JSON-encoded list of e-tags in thecontentfield of the response. Weird, but ok. Stop the subscription in your "dvm" terminal and respond to your "client" with a recommendation to read my first note:bash nak event -k 6300 -t e=a65665a3a4ca2c0d7b7582f4f0d073cd1c83741c25a07e98d49a43e46d258caf -c '[["e","214f5898a7b75b7f95d9e990b706758ea525fe86db54c1a28a0f418c357f9b08","wss://nos.lol/"]]' nos.lolHere's the response event we're sending:
json { "kind": 6300, "id": "bb5f38920cbca15d3c79021f7d0051e82337254a84c56e0f4182578e4025232e", "pubkey": "79be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798", "created_at": 1739408411, "tags": [ ["e", "a65665a3a4ca2c0d7b7582f4f0d073cd1c83741c25a07e98d49a43e46d258caf"] ], "content": "[[\"e\",\"214f5898a7b75b7f95d9e990b706758ea525fe86db54c1a28a0f418c357f9b08\",\"wss://nos.lol/\"]]", "sig": "a0fe2c3419c5c54cf2a6d9a2a5726b2a5b766d3c9e55d55568140979354003aacb038e90bdead43becf5956faa54e3b60ff18c0ea4d8e7dfdf0c8dd97fb24ff9" }Notice the
etag targets our original request.This should result in the job result event showing up in our "client" terminal. Success!
If something isn't working, I've also create a video of the full process with some commentary which you can find here.
Note that in practice, DVMs can be much more picky about the requests they will respond to, due to implementations failing to follow Postel's law. Hopefully that will improve over time. For now, here are a few resources that are useful when working with or developing DVMs:
Conclusion
I started this post by hinting that DVMs might be as fundamental as relays are to making nostr work. But (apart from the fact that we'd end up with an acronym like DVMNOSTRZ+*, which would only exascerbate the pronounciation wars (if such a thing were possible)), that's not exactly true.
DVMs have emerged as a central paradigm in the nostr world because they're a generalization of a design pattern unique to nostr's architecture - but which exists in many other places, including NIP 46 signer flows and NIP 47 wallet connect. Each of these sub-protocols works by using relays as neutral brokers for requests in order to avoid coupling services to web addresses.
This approach has all kinds of neat benefits, not least of which is allowing service providers to host their software without having to accept incoming TCP connections. But it's really an emergent property of relays, which not only are useful for brokering communication between users (aka storing events), but also brokering communication between machines.
The possibilities of this architecture have only started to emerge, so be on the lookout for new applications, and don't be afraid to experiment - just please, don't serialize json inside json 🤦♂️
-
 @ e3ba5e1a:5e433365
2025-02-13 06:16:49
@ e3ba5e1a:5e433365
2025-02-13 06:16:49My favorite line in any Marvel movie ever is in “Captain America.” After Captain America launches seemingly a hopeless assault on Red Skull’s base and is captured, we get this line:
“Arrogance may not be a uniquely American trait, but I must say, you do it better than anyone.”
Yesterday, I came across a comment on the song Devil Went Down to Georgia that had a very similar feel to it:

America has seemingly always been arrogant, in a uniquely American way. Manifest Destiny, for instance. The rest of the world is aware of this arrogance, and mocks Americans for it. A central point in modern US politics is the deriding of racist, nationalist, supremacist Americans.
That’s not what I see. I see American Arrogance as not only a beautiful statement about what it means to be American. I see it as an ode to the greatness of humanity in its purest form.
For most countries, saying “our nation is the greatest” is, in fact, twinged with some level of racism. I still don’t have a problem with it. Every group of people should be allowed to feel pride in their accomplishments. The destruction of the human spirit since the end of World War 2, where greatness has become a sin and weakness a virtue, has crushed the ability of people worldwide to strive for excellence.
But I digress. The fears of racism and nationalism at least have a grain of truth when applied to other nations on the planet. But not to America.
That’s because the definition of America, and the prototype of an American, has nothing to do with race. The definition of Americanism is freedom. The founding of America is based purely on liberty. On the God-given rights of every person to live life the way they see fit.
American Arrogance is not a statement of racial superiority. It’s barely a statement of national superiority (though it absolutely is). To me, when an American comments on the greatness of America, it’s a statement about freedom. Freedom will always unlock the greatness inherent in any group of people. Americans are definitionally better than everyone else, because Americans are freer than everyone else. (Or, at least, that’s how it should be.)
In Devil Went Down to Georgia, Johnny is approached by the devil himself. He is challenged to a ridiculously lopsided bet: a golden fiddle versus his immortal soul. He acknowledges the sin in accepting such a proposal. And yet he says, “God, I know you told me not to do this. But I can’t stand the affront to my honor. I am the greatest. The devil has nothing on me. So God, I’m gonna sin, but I’m also gonna win.”
Libertas magnitudo est
-
 @ 8cb60e21:5f2deaea
2024-08-09 14:55:19
@ 8cb60e21:5f2deaea
2024-08-09 14:55:19To prevent the contentIds from being undefined and causing an error, you can add handling to check if contentIds is defined before using it. Additionally, ensure contentIds has been fetched and is not in the loading state before proceeding with the fetchResourcesFromNDK function. Here is the updated useResourcesQuery with the necessary error handling
```js import { useState, useEffect } from 'react'; import { useQuery } from '@tanstack/react-query'; import { useNDKContext } from '@/context/NDKContext'; import { useContentIdsQuery } from '@/hooks/apiQueries/useContentIdsQuery';
const AUTHOR_PUBKEY = process.env.NEXT_PUBLIC_AUTHOR_PUBKEY;
export function useResourcesQuery() { const [isClient, setIsClient] = useState(false);
const { contentIds, contentIdsLoading, contentIdsError, refetchContentIds } = useContentIdsQuery(); const ndk = useNDKContext(); useEffect(() => { setIsClient(true); }, []); useEffect(() => { refetchContentIds(); }, [refetchContentIds]); const hasRequiredProperties = (event) => { if (!contentIds) { return false; } const hasPlebDevs = event.tags.some(([tag, value]) => tag === "t" && value === "plebdevs"); const hasWorkshop = event.tags.some(([tag, value]) => tag === "t" && value === "resource"); const hasId = contentIds.includes(event.id); return hasPlebDevs && hasWorkshop && hasId; }; const fetchResourcesFromNDK = async () => { try { if (contentIdsLoading) { return []; // or a loading state indication } if (contentIdsError) { console.error('Error fetching content IDs:', contentIdsError); return []; } if (!contentIds) { return []; } console.log('Fetching workshops from NDK'); await ndk.connect(); const filter = { kinds: [30023, 30402], authors: [AUTHOR_PUBKEY] }; const events = await ndk.fetchEvents(filter); if (events && events.size > 0) { const eventsArray = Array.from(events); console.log('eventsArray', eventsArray); const resources = eventsArray.filter(event => hasRequiredProperties(event)); return resources; } return []; } catch (error) { console.error('Error fetching workshops from NDK:', error); return []; } }; const { data: resources, isLoading: resourcesLoading, error: resourcesError, refetch: refetchResources } = useQuery({ queryKey: ['resources', isClient], queryFn: fetchResourcesFromNDK, staleTime: 1000 * 60 * 30, // 30 minutes refetchInterval: 1000 * 60 * 30, // 30 minutes enabled: isClient, }); return { resources, resourcesLoading, resourcesError, refetchResources };} ```
Explanation:
Error Handling for contentIds: Added checks to ensure contentIds is defined before using it. If contentIds is still loading or an error occurred while fetching contentIds, handle these cases appropriately by returning empty arrays or logging the error. Loading State Check: If contentIds is still loading, the fetchResourcesFromNDK function will return an empty array or indicate a loading state. Error Check: If there's an error in fetching contentIds, log the error and return an empty array to avoid breaking the application flow.Apply the Same Handling to useCoursesQuery
Similarly, you can apply the same error handling and checks in the useCoursesQuery function:
```js import { useState, useEffect } from 'react'; import { useQuery } from '@tanstack/react-query'; import { useNDKContext } from '@/context/NDKContext'; import { useContentIdsQuery } from '@/hooks/apiQueries/useContentIdsQuery';
const AUTHOR_PUBKEY = process.env.NEXT_PUBLIC_AUTHOR_PUBKEY;
export function useCoursesQuery() { const [isClient, setIsClient] = useState(false);
const { contentIds, contentIdsLoading, contentIdsError, refetchContentIds } = useContentIdsQuery(); const ndk = useNDKContext(); useEffect(() => { setIsClient(true); }, []); useEffect(() => { refetchContentIds(); }, [refetchContentIds]); const hasRequiredProperties = (event) => { if (!contentIds) { return false; } const hasCourseTag = event.tags.some(([tag, value]) => tag === "t" && value === "course"); const hasId = contentIds.includes(event.id); return hasCourseTag && hasId; }; const fetchCoursesFromNDK = async () => { try { if (contentIdsLoading) { return []; // or a loading state indication } if (contentIdsError) { console.error('Error fetching content IDs:', contentIdsError); return []; } if (!contentIds) { return []; } console.log('Fetching courses from NDK'); await ndk.connect(); const filter = { kinds: [30004], authors: [AUTHOR_PUBKEY] }; const events = await ndk.fetchEvents(filter); if (events && events.size > 0) { const eventsArray = Array.from(events); console.log('eventsArray', eventsArray); const courses = eventsArray.filter(event => hasRequiredProperties(event)); return courses; } return []; } catch (error) { console.error('Error fetching courses from NDK:', error); return []; } }; const { data: courses, isLoading: coursesLoading, error: coursesError, refetch: refetchCourses } = useQuery({ queryKey: ['courses', isClient], queryFn: fetchCoursesFromNDK, staleTime: 1000 * 60 * 30, // 30 minutes refetchInterval: 1000 * 60 * 30, // 30 minutes enabled: isClient, }); return { courses, coursesLoading, coursesError, refetchCourses };} ``` By incorporating these changes, you should be able to prevent errors related to contentIds being undefined and ensure a smoother data-fetching process.
-
 @ b1ddb4d7:471244e7
2025-05-24 11:00:40
@ b1ddb4d7:471244e7
2025-05-24 11:00:40The upcoming Bitcoin 2025 conference, scheduled from May 27–29 at the Venetian Conference Center in Las Vegas, is set to make history with an official attempt to break the GUINNESS WORLD RECORDS® title for the most Bitcoin point-of-sale transactions in an eight-hour period.
Organized by BTC Inc, the event will showcase Bitcoin’s evolution from a digital capital asset to a practical medium of exchange, leveraging the latest advancements in payment technology.
Tap-to-Pay with Lightning-Ready Bolt Cards
To facilitate this record-setting attempt, 4,000 Lightning-ready Bolt Cards will be distributed to conference attendees.
— Uncle Rockstar Developer (@r0ckstardev) May 15, 2025
These NFC-enabled cards allow users to make instant, contactless Bitcoin payments at vendor booths throughout the expo-no apps or QR codes required, just a simple tap.
The cards are available in four collectible designs, each featuring a prominent figure in Bitcoin’s history: Senator Cynthia Lummis, Michael Saylor, Satoshi Nakamoto, and Jack Dorsey.
Each attendee will receive a randomly assigned card, making them both functional and collectible souvenirs.
Senator Lummis: A Playful Provocation
Notably, one of the card designs features Senator Cynthia Lummis with laser eyes-a playful nod to her reputation as a leading Bitcoin advocate in US politics.
While Lummis is known for her legislative efforts to promote Bitcoin integration, she has publicly stated she prefers to “spend dollars and save Bitcoin,” viewing BTC as a long-term store of value rather than a daily currency.
The choice to feature her on the Bolt Card, could be suggested by Rockstar Dev of the BTC Pay Server Foundation, perhaps a lighthearted way to highlight the ongoing debate about Bitcoin’s role in everyday payments.
Nothing cracks me up quite like a senator that wants the US to buy millions of Bitcoin use dollars to buy a beer at a Bitcoin bar.
This is how unserious some of you are. pic.twitter.com/jftIEggmip
— Magoo PhD (@HodlMagoo) April 4, 2025
How Bolt Cards and the Lightning Network Work
Bolt Cards are physical cards equipped with NFC (Near Field Communication) technology, similar to contactless credit or debit cards. When linked to a compatible Lightning wallet, they enable users to make Bitcoin payments over the Lightning Network by simply tapping the card at a point-of-sale terminal.
The Lightning Network is a second-layer protocol built on top of Bitcoin, designed to facilitate instant, low-cost transactions ideal for everyday purchases.
This integration aims to make Bitcoin as easy to use as traditional payment methods, eliminating the need for QR code scanning or mobile apps.
A Showcase for Bitcoin’s Real-World Usability
With over 30,000 attendees, 300 exhibitors, and 500 speakers expected, the Bitcoin 2025 conference is poised to be the largest Bitcoin event of the year-and potentially the most transactional.
The event will feature on-site activations such as the Official Bitcoin Magazine Store, where all merchandise will be available at a 21% discount for those paying with Bitcoin via the Lightning Network-a nod to Bitcoin’s 21 million coin supply limit.
By deeply integrating Lightning payments into the conference experience, organizers hope to demonstrate Bitcoin’s readiness for mainstream commerce and set a new benchmark for its practical use as a currency.
Conclusion
The Guinness World Record attempt at Bitcoin 2025 is more than a publicity stunt-it’s a bold demonstration of Bitcoin’s technological maturity and its potential to function as a modern, everyday payment method.
Whether or not the record is set, the event will serve as a milestone in the ongoing journey to make Bitcoin a truly global, user-friendly currency
-
 @ 8cb60e21:5f2deaea
2024-08-09 14:53:43
@ 8cb60e21:5f2deaea
2024-08-09 14:53:43To prevent the contentIds from being undefined and causing an error, you can add handling to check if contentIds is defined before using it. Additionally, ensure contentIds has been fetched and is not in the loading state before proceeding with the fetchResourcesFromNDK function. Here is the updated useResourcesQuery with the necessary error handling
```js import { useState, useEffect } from 'react'; import { useQuery } from '@tanstack/react-query'; import { useNDKContext } from '@/context/NDKContext'; import { useContentIdsQuery } from '@/hooks/apiQueries/useContentIdsQuery';
const AUTHOR_PUBKEY = process.env.NEXT_PUBLIC_AUTHOR_PUBKEY;
export function useResourcesQuery() { const [isClient, setIsClient] = useState(false);
const { contentIds, contentIdsLoading, contentIdsError, refetchContentIds } = useContentIdsQuery(); const ndk = useNDKContext(); useEffect(() => { setIsClient(true); }, []); useEffect(() => { refetchContentIds(); }, [refetchContentIds]); const hasRequiredProperties = (event) => { if (!contentIds) { return false; } const hasPlebDevs = event.tags.some(([tag, value]) => tag === "t" && value === "plebdevs"); const hasWorkshop = event.tags.some(([tag, value]) => tag === "t" && value === "resource"); const hasId = contentIds.includes(event.id); return hasPlebDevs && hasWorkshop && hasId; }; const fetchResourcesFromNDK = async () => { try { if (contentIdsLoading) { return []; // or a loading state indication } if (contentIdsError) { console.error('Error fetching content IDs:', contentIdsError); return []; } if (!contentIds) { return []; } console.log('Fetching workshops from NDK'); await ndk.connect(); const filter = { kinds: [30023, 30402], authors: [AUTHOR_PUBKEY] }; const events = await ndk.fetchEvents(filter); if (events && events.size > 0) { const eventsArray = Array.from(events); console.log('eventsArray', eventsArray); const resources = eventsArray.filter(event => hasRequiredProperties(event)); return resources; } return []; } catch (error) { console.error('Error fetching workshops from NDK:', error); return []; } }; const { data: resources, isLoading: resourcesLoading, error: resourcesError, refetch: refetchResources } = useQuery({ queryKey: ['resources', isClient], queryFn: fetchResourcesFromNDK, staleTime: 1000 * 60 * 30, // 30 minutes refetchInterval: 1000 * 60 * 30, // 30 minutes enabled: isClient, }); return { resources, resourcesLoading, resourcesError, refetchResources };} ```
Explanation:
Error Handling for contentIds: Added checks to ensure contentIds is defined before using it. If contentIds is still loading or an error occurred while fetching contentIds, handle these cases appropriately by returning empty arrays or logging the error. Loading State Check: If contentIds is still loading, the fetchResourcesFromNDK function will return an empty array or indicate a loading state. Error Check: If there's an error in fetching contentIds, log the error and return an empty array to avoid breaking the application flow.Apply the Same Handling to useCoursesQuery
Similarly, you can apply the same error handling and checks in the useCoursesQuery function:
```js import { useState, useEffect } from 'react'; import { useQuery } from '@tanstack/react-query'; import { useNDKContext } from '@/context/NDKContext'; import { useContentIdsQuery } from '@/hooks/apiQueries/useContentIdsQuery';
const AUTHOR_PUBKEY = process.env.NEXT_PUBLIC_AUTHOR_PUBKEY;
export function useCoursesQuery() { const [isClient, setIsClient] = useState(false);
const { contentIds, contentIdsLoading, contentIdsError, refetchContentIds } = useContentIdsQuery(); const ndk = useNDKContext(); useEffect(() => { setIsClient(true); }, []); useEffect(() => { refetchContentIds(); }, [refetchContentIds]); const hasRequiredProperties = (event) => { if (!contentIds) { return false; } const hasCourseTag = event.tags.some(([tag, value]) => tag === "t" && value === "course"); const hasId = contentIds.includes(event.id); return hasCourseTag && hasId; }; const fetchCoursesFromNDK = async () => { try { if (contentIdsLoading) { return []; // or a loading state indication } if (contentIdsError) { console.error('Error fetching content IDs:', contentIdsError); return []; } if (!contentIds) { return []; } console.log('Fetching courses from NDK'); await ndk.connect(); const filter = { kinds: [30004], authors: [AUTHOR_PUBKEY] }; const events = await ndk.fetchEvents(filter); if (events && events.size > 0) { const eventsArray = Array.from(events); console.log('eventsArray', eventsArray); const courses = eventsArray.filter(event => hasRequiredProperties(event)); return courses; } return []; } catch (error) { console.error('Error fetching courses from NDK:', error); return []; } }; const { data: courses, isLoading: coursesLoading, error: coursesError, refetch: refetchCourses } = useQuery({ queryKey: ['courses', isClient], queryFn: fetchCoursesFromNDK, staleTime: 1000 * 60 * 30, // 30 minutes refetchInterval: 1000 * 60 * 30, // 30 minutes enabled: isClient, }); return { courses, coursesLoading, coursesError, refetchCourses };} ``` By incorporating these changes, you should be able to prevent errors related to contentIds being undefined and ensure a smoother data-fetching process.
-
 @ 97c70a44:ad98e322
2025-02-03 22:25:35
@ 97c70a44:ad98e322
2025-02-03 22:25:35Last week, in a bid to understand the LLM hype, I decided to write a trivial nostr-related program in rust via a combination of codebuff (yes, that is a referral link, pls click), aider, and goose.
The result of the experiment was inconclusive, but as a side effect it produced a great case study in converting a NINO into a Real Nostr App.
Introducing Roz
Roz, a friendly notary for nostr events.
To use it, simply publish an event to
relay.damus.ioornos.lol, and roz will make note of it. To find out when roz first saw a given event, just ask:curl https://roz.coracle.social/notary/cb429632ae22557d677a11149b2d0ccd72a1cf66ac55da30e3534ed1a492765dThis will return a JSON payload with a
seenkey indicating when roz first saw the event. How (and whether) you use this is up to you!De-NINO-fying roz
Roz is just a proof of concept, so don't rely on it being there forever. And anyway, roz is a NINO, since it provides value to nostr (potentially), but doesn't really do things in a nostr-native way. It also hard-codes its relays, and certainly doesn't use the outbox model or sign events. But that's ok, it's a proof of concept.
A much better way to do this would be to modify roz to properly leverage nostr's capabilities, namely:
- Use nostr-native data formats (i.e., draft a new kind)
- Use relays instead of proprietary servers for data storage
- Leverage nostr identities and signatures to decouple trust from storage, and allow trusted attestations to be discovered
Luckily, this is not hard at all. In fact, I've gone ahead and drafted a PR to the NIPs repo that adds timestamp annotations to NIP 03, as an alternative to OpenTimestamps. The trade-off is that while user attestations are far less reliable than OTS proofs, they're much easier to verify, and can reach a pretty high level of reliability by combining multiple attestation sources with other forms of reputation.
In other words, instead of going nuclear and embedding your attestations into The Time Chain, you can simply ask 5-10 relays or people you trust for their attestations for a given event.
This PR isn't terribly important on its own, but it does remove one small barrier between us and trusted key rotation events (or other types of event that require establishing a verifiable chain of causality).