-
 @ d9c98e71:37007462
2025-05-22 09:48:20
@ d9c98e71:37007462
2025-05-22 09:48:20„Man muss noch Chaos in sich haben, um einen tanzenden Stern gebären zu können.“
– Friedrich Nietzsche
Der Mensch wächst nicht aus der Welt – er wird in sie geworfen, ohne Ursprung, ohne Auftrag, ohne Trost. Die Familie erscheint zuerst als Halt, doch sie ist oft der erste Spiegel, in dem man sich selbst nicht erkennt. Man nennt es Liebe, nennt es Bindung – aber vielleicht ist es nur die stille Einweisung in ein Gefängnis, dessen Mauern wie Umarmungen aussehen.
Das Kind ist nicht die Fortsetzung des Selbst, sondern der Beweis, dass auch das Chaos Nachwuchs hat. Es lacht, weil es noch nicht weiß, was Lachen kostet. Es fragt nicht, weil es noch nicht weiß, dass Fragen selten Antworten finden. Und doch ist es das Kind, das die Ordnung zum Wanken bringt – nicht durch Widerstand, sondern durch seine unbestechliche Gegenwärtigkeit.
Freiheit beginnt dort, wo man aufhört, sich retten zu lassen. Sie ist kein Zustand, sondern eine Haltung: die Weigerung, sich einer Bedeutung zu unterwerfen, die von außen kommt. Die Welt verlangt Funktion – das freie Leben verweigert sich der Funktion, nicht durch Aufstand, sondern durch Abwesenheit. Wer Sicherheit sucht, hat die Welt bereits verloren.
Einsamkeit ist kein Unglück – sie ist der Boden, auf dem das Selbst sich überhaupt erst spüren kann. Sie ist nicht leer, sondern ungeteilt. Was fehlt, ist nicht ein anderer Mensch, sondern die Illusion, dass Nähe uns vollständig machen könnte. In der Tiefe des Alleinseins offenbart sich nicht Mangel, sondern Klarheit.
Ein Kind stellt keine Fragen über das Nichts – es lebt in ihm, ohne es zu wissen. Der Erwachsene aber erkennt es, spürt es wie eine zweite Haut, die nicht abgelegt werden kann. Doch dieses Wissen ist keine Strafe. Es ist die Bedingung jeder echten Handlung. Wer das Nichts kennt, liebt nicht, um sich zu retten – sondern weil er weiß, dass nichts gerettet werden muss.
Ein Leben im Angesicht der Leere ist möglich. Nicht durch Verdrängung, sondern durch Durchschreiten. Die Rolle, die man spielt, wird erträglich, wenn man sie nicht mit Identität verwechselt. Die Arbeit, die man verrichtet, dient nicht mehr dem Fortschritt, sondern der Form – und vielleicht liegt darin schon Würde genug.
Familie kann ein Nest sein – oder ein Netz. Es hält, oder es hält fest. Doch auch das Netz kann Heimat sein, wenn man nicht mehr erwartet, darin zu fliegen. Ein Kind zu begleiten heißt nicht, ihm Wahrheit zu geben, sondern ihm Raum zu lassen, seine eigene zu verwerfen.
Freiheit ist kein Ziel, sondern ein Aufhören. Wer nichts mehr will, dem kann nichts genommen werden. Wer das Nichts annimmt, dem begegnet keine Leere mehr – sondern Raum. In diesem Raum entsteht das, was nicht geplant ist, nicht beherrscht und nicht gezählt: der Moment, das Staunen, die Stille zwischen zwei Gedanken. Vielleicht ist genau das genug.
Man kann leben mit dem Nichts – wenn man nicht mehr verlangt, dass es Sinn macht. Man kann Vater sein, Mutter, Freund, Fremder – ohne sich zu verlieren. Man kann lachen, weinen, müde sein – ohne Trost zu brauchen. Denn wer dem Nichts ins Auge gesehen hat, weiß: Alles ist bedeutungslos. Und genau deshalb ist alles erlaubt. Und manchmal, ganz selten, auch: schön.
-
 @ d9c98e71:37007462
2025-05-22 09:48:10
@ d9c98e71:37007462
2025-05-22 09:48:10„Die Tatsache, dass das Leben keinen Sinn hat, ist ein Grund zu leben – und zwar der einzige.“
– Emil Cioran
Der Mensch steht im Zentrum eines Raumes, der sich weigert, eine Mitte zu haben. Alles um ihn herum scheint geordnet, doch diese Ordnung ist ein leises Zittern vor dem Chaos, das jede Struktur unterwandert. Es gibt kein Versprechen, das nicht gebrochen wird, kein Licht, das nicht aus einer tieferen Dunkelheit geboren wird. So flackert die Existenz – ein schwankender Schein über einem Abgrund, der kein Echo zurückgibt.
Das Nichts ist nicht Abwesenheit. Es ist Gegenwart ohne Form. Es liegt nicht hinter den Dingen, sondern in ihnen – wie ein Geruch, der bleibt, wenn alle Türen geschlossen sind. Es ist der unsichtbare Kern der Welt, der Grund, warum jedes Wort in sich selbst zerfällt, jede Bewegung zu spät kommt, jeder Sinn sich verflüchtigt, sobald man ihn greifen will. Das Schweigen des Universums ist keine Antwort – es ist die endgültige Form der Gleichgültigkeit.
Wer dem Nichts begegnet, verliert nicht die Hoffnung – er erkennt, dass es nie Hoffnung gab, sondern nur das Bedürfnis danach. Die Leere ist kein Loch, das gefüllt werden will, sondern ein Zustand, der alles durchdringt. Man lebt nicht trotz des Nichts – man lebt im Nichts, als Ahnung, als Abdruck, als Fußspur im Staub eines Raums, den niemand betritt.
Melancholie ist kein Gefühl, sondern ein Aggregatzustand des Bewusstseins, das zu viel gesehen hat, um noch zu glauben. Sie trägt kein Schwarz, sie schreit nicht. Sie fließt durch uns wie ein langsamer Strom, der die Farben der Dinge auswäscht. In ihr liegt kein Wunsch nach Erlösung, sondern nur das Wissen, dass selbst Erlösung eine weitere Form von Fessel wäre. Man kehrt nicht heim, man löst sich auf – langsam, leise, endgültig.
Der Tod ist nicht der Feind des Lebens, sondern seine Form. Leben ist der Prozess des langsamen Verschwindens, und Sterben ist nur die letzte Geste einer Bewegung, die längst begonnen hat. Die Zeit nimmt nicht, sie löscht. Sie lässt zurück, was nicht mehr gefüllt werden kann: ein Umriss, eine Hülle, ein Bild ohne Substanz. Der Mensch verliert sich nicht am Ende, sondern in jedem Moment, den er durchschreitet.
Erinnerung ist kein Besitz, sondern eine Wunde. Was zurückblickt, blickt durch einen zerbrochenen Spiegel – jedes Fragment spiegelt etwas, aber nie das Ganze. Und wer sich darin sucht, findet nicht sich selbst, sondern die Lücken zwischen den Bildern. Vergangenheit ist nicht, was war, sondern das, was nie ganz war – und deshalb nie ganz vergeht.
Existenz ist ein Exil. Nicht von einem Ort, sondern von sich selbst. Man ist sich nicht nahe, man ist sich fremd – und in dieser Fremdheit liegt keine Tragik, sondern ein nüchterner Frieden. Einsamkeit ist kein Zustand, sondern die einzig mögliche Beziehung zur Welt. Alles andere ist Täuschung – ein letzter Versuch, das Unvereinbare zu versöhnen.
Sinn verflüchtigt sich mit jeder Geste, die ihn zu fassen sucht. Je näher man kommt, desto mehr löst er sich auf – wie Nebel vor der Hand. Was bleibt, ist das Bild der Suche selbst, eine Bewegung im Leeren. Man begreift nicht – man kreist. Und in diesem Kreis liegt der Kern der Erfahrung: nicht das Ziel, sondern die Auflösung aller Ziele.
Die einzige Freiheit liegt nicht im Handeln, sondern im Entgleiten. Der Verzicht auf Bedeutung, auf Richtung, auf Rettung – das ist der erste Akt der Selbstermächtigung. Nicht laut, nicht kämpferisch, sondern als stilles Hinwegtreten aus dem Spiel. Dort beginnt das, was nicht mehr genommen werden kann: die Unabhängigkeit vom Verlangen.
Nichts bleibt. Und gerade deshalb geschieht alles. Nicht um zu sein, sondern um zu vergehen. Und vielleicht liegt darin die letzte Schönheit – nicht im Bestehen, sondern im Verlöschen. In der Fähigkeit, in Ketten zu tanzen, wissend, dass jede Kette aus Licht besteht, das schon lange erloschen ist.
-
 @ 21335073:a244b1ad
2025-05-21 16:58:36
@ 21335073:a244b1ad
2025-05-21 16:58:36The other day, I had the privilege of sitting down with one of my favorite living artists. Our conversation was so captivating that I felt compelled to share it. I’m leaving his name out for privacy.
Since our last meeting, I’d watched a documentary about his life, one he’d helped create. I told him how much I admired his openness in it. There’s something strange about knowing intimate details of someone’s life when they know so little about yours—it’s almost like I knew him too well for the kind of relationship we have.
He paused, then said quietly, with a shy grin, that watching the documentary made him realize how “odd and eccentric” he is. I laughed and told him he’s probably the sanest person I know. Because he’s lived fully, chasing love, passion, and purpose with hardly any regrets. He’s truly lived.
Today, I turn 44, and I’ll admit I’m a bit eccentric myself. I think I came into the world this way. I’ve made mistakes along the way, but I carry few regrets. Every misstep taught me something. And as I age, I’m not interested in blending in with the world—I’ll probably just lean further into my own brand of “weird.” I want to live life to the brim. The older I get, the more I see that the “normal” folks often seem less grounded than the eccentric artists who dare to live boldly. Life’s too short to just exist, actually live.
I’m not saying to be strange just for the sake of it. But I’ve seen what the crowd celebrates, and I’m not impressed. Forge your own path, even if it feels lonely or unpopular at times.
It’s easy to scroll through the news and feel discouraged. But actually, this is one of the most incredible times to be alive! I wake up every day grateful to be here, now. The future is bursting with possibility—I can feel it.
So, to my fellow weirdos on nostr: stay bold. Keep dreaming, keep pushing, no matter what’s trending. Stay wild enough to believe in a free internet for all. Freedom is radical—hold it tight. Live with the soul of an artist and the grit of a fighter. Thanks for inspiring me and so many others to keep hoping. Thank you all for making the last year of my life so special.
-
 @ a19caaa8:88985eaf
2025-05-05 02:55:57
@ a19caaa8:88985eaf
2025-05-05 02:55:57↓ジャック(twitter創業者)のツイート nostr:nevent1qvzqqqqqqypzpq35r7yzkm4te5460u00jz4djcw0qa90zku7739qn7wj4ralhe4zqy28wumn8ghj7un9d3shjtnyv9kh2uewd9hsqg9cdxf7s7kg8kj70a4v5j94urz8kmel03d5a47tr4v6lx9umu3c95072732
↓それに絡むたゃ nostr:note1hr4m0d2k2cvv0yg5xtmpuma0hsxfpgcs2lxe7vlyhz30mfq8hf8qp8xmau
↓たゃのひとりごと nostr:nevent1qqsdt9p9un2lhsa8n27y7gnr640qdjl5n2sg0dh4kmxpqget9qsufngsvfsln nostr:note14p9prp46utd3j6mpqwv46m3r7u7cz6tah2v7tffjgledg5m4uy9qzfc2zf
↓有識者様の助言 nostr:nevent1qvzqqqqqqypzpujqe8p9zrpuv0f4ykk3rmgnqa6p6r0lan0t8ewd0ksj89kqcz5xqqst8w0773wxnkl8sn94tvmd3razcvms0kxjwe00rvgazp9ljjlv0wq0krtvt nostr:nevent1qvzqqqqqqypzpujqe8p9zrpuv0f4ykk3rmgnqa6p6r0lan0t8ewd0ksj89kqcz5xqqsxchzm7s7vn8a82q40yss3a84583chvd9szl9qc3w5ud7pr9ugengcgt9qx
↓たゃ nostr:nevent1qqsp2rxvpax6ks45tuzhzlq94hq6qtm47w69z8p5wepgq9u4txaw88s554jkd
-
 @ f11e91c5:59a0b04a
2025-04-30 07:52:21
@ f11e91c5:59a0b04a
2025-04-30 07:52:21!!!2022-07-07に書かれた記事です。
暗号通貨とかでお弁当売ってます 11:30〜14:00ぐらいでやってます
◆住所 木曜日・東京都渋谷区宇田川町41 (アベマタワーの下らへん)
◆お値段
Monacoin 3.9mona
Bitzeny 390zny
Bitcoin 3900sats (#lightningNetwork)
Ethereum 0.0039Ether(#zkSync)
39=thank you. (円を基準にしてません)
最近は週に一回になりました。 他の日はキッチンカーの現場を探したり色々してます。 東京都内で平日ランチ出店出来そうな場所があればぜひご連絡を!
 写真はNFCタグです。
スマホにウォレットがあればタッチして3900satsで決済出来ます。
正直こんな怪しい手書きのNFCタグなんて絶対にビットコイナーは触りたくも無いだろうなと思いますが、これでも良いんだぜというメッセージです。
写真はNFCタグです。
スマホにウォレットがあればタッチして3900satsで決済出来ます。
正直こんな怪しい手書きのNFCタグなんて絶対にビットコイナーは触りたくも無いだろうなと思いますが、これでも良いんだぜというメッセージです。今までbtcpayのposでしたが速度を追求してこれに変更しました。 たまに上手くいかないですがそしたら渋々POS出すので温かい目でよろしくお願いします。
ノードを建てたり決済したりで1年経ちました。 最近も少しずつノードを建てる方が増えてるみたいで本当凄いですねUmbrel 大体の人がルーティングに果敢に挑むのを見つつ 奥さんに土下座しながら費用を捻出する弱小の私は決済の利便性を全開で振り切るしか無いので応援よろしくお願いします。
あえて あえて言うのであれば、ルーティングも楽しいですけど やはり本当の意味での即時決済や相手を選んでチャネルを繋げる楽しさもあるよとお伝えしたいっ!! 決済を受け入れないと分からない所ですが 承認がいらない時点で画期的です。
QRでもタッチでも金額指定でも入力でも もうやりようには出来てしまうし進化が恐ろしく早いので1番利用の多いpaypayの手数料(事業者側のね)を考えたらビットコイン凄いじゃない!と叫びたくなる。 が、やはり税制面や価格の変動(うちはBTC固定だけども)ウォレットの操作や普及率を考えるとまぁ難しい所もあるんですかね。
それでも継続的に沢山の人が色んな活動をしてるので私も何か出来ることがあれば 今後も奥さんに土下座しながら頑張って行きたいと思います。
(Originally posted 2022-07-07)
I sell bento lunches for cryptocurrency. We’re open roughly 11:30 a.m. – 2:00 p.m. Address Thursdays – 41 Udagawa-chō, Shibuya-ku, Tokyo (around the base of Abema Tower)
Prices Coin Price Note Monacoin 3.9 MONA
Bitzeny 390 ZNY Bitcoin 3,900 sats (Lightning Network)
Ethereum 0.0039 ETH (zkSync) “39” sounds like “thank you” in Japanese. Prices aren’t pegged to yen.These days I’m open only once a week. On other days I’m out scouting new spots for the kitchen-car. If you know weekday-lunch locations inside Tokyo where I could set up, please let me know!
The photo shows an NFC tag. If your phone has a Lightning wallet, just tap and pay 3,900 sats. I admit this hand-written NFC tag looks shady—any self-respecting Bitcoiner probably wouldn’t want to tap it—but the point is: even this works!
I used to run a BTCPay POS, but I switched to this setup for speed. Sometimes the tap payment fails; if that happens I reluctantly pull out the old POS. Thanks for your patience.
It’s been one year since I spun up a node and started accepting Lightning payments. So many people are now running their own nodes—Umbrel really is amazing. While the big players bravely chase routing fees, I’m a tiny operator scraping together funds while begging my wife for forgiveness, so I’m all-in on maximising payment convenience. Your support means a lot!
If I may add: routing is fun, but instant, trust-minimised payments and the thrill of choosing whom to open channels with are just as exciting. You’ll only understand once you start accepting payments yourself—zero-confirmation settlement really is revolutionary.
QR codes, NFC taps, fixed amounts, manual entry… the possibilities keep multiplying, and the pace of innovation is scary fast. When I compare it to the merchant fees on Japan’s most-used service, PayPay, I want to shout: “Bitcoin is incredible!” Sure, taxes, price volatility (my shop is BTC-denominated, though), wallet UX, and adoption hurdles are still pain points.
Even so, lots of people keep building cool stuff, so I’ll keep doing what I can—still on my knees to my wife, but moving forward!
-
 @ ec42c765:328c0600
2025-02-05 23:45:09
@ ec42c765:328c0600
2025-02-05 23:45:09test
test
-
 @ ec42c765:328c0600
2025-02-05 23:43:35
@ ec42c765:328c0600
2025-02-05 23:43:35test
-
 @ fa984bd7:58018f52
2025-05-21 09:51:34
@ fa984bd7:58018f52
2025-05-21 09:51:34This post has been deleted.
-
 @ c9badfea:610f861a
2025-05-20 19:49:20
@ c9badfea:610f861a
2025-05-20 19:49:20- Install Sky Map (it's free and open source)
- Launch the app and tap Accept, then tap OK
- When asked to access the device's location, tap While Using The App
- Tap somewhere on the screen to activate the menu, then tap ⁝ and select Settings
- Disable Send Usage Statistics
- Return to the main screen and enjoy stargazing!
ℹ️ Use the 🔍 icon in the upper toolbar to search for a specific celestial body, or tap the 👁️ icon to activate night mode
-
 @ d9c98e71:37007462
2025-05-22 09:47:53
@ d9c98e71:37007462
2025-05-22 09:47:53„Wahrheit ist kein Besitz, den man verteidigt, sondern ein Prozess, den man gemeinsam gestaltet.“
– frei nach dem Geist freier Netzwerke und resilienter Systeme
Bitcoin ist mehr als nur ein monetäres Protokoll. Es ist ein kulturelles Artefakt, ein philosophisches Statement und ein praktischer Ausdruck radikaler Souveränität, kollektiver Verantwortung und struktureller Ethik. Wer Bitcoin ausschließlich als technologisches Experiment oder ökonomisches Asset betrachtet, verfehlt seine tiefere Bedeutung: Bitcoin ist eine politische Philosophie – nicht in Büchern niedergeschrieben, sondern in Code gegossen. Eine Philosophie, die nicht behauptet, die Wahrheit zu kennen, sondern eine Methode zur gemeinsamen Verifikation. Eine Philosophie des Konsenses.
Im Zentrum dieser Philosophie steht die Einsicht, dass Legitimität nicht von oben gewährt, sondern von unten erzeugt wird. Keine zentrale Instanz entscheidet, was gilt. Keine Autorität garantiert Vertrauen. Stattdessen entsteht alles aus einem gemeinsamen, freiwilligen Prozess: offen, nachvollziehbar, überprüfbar. Bitcoin ersetzt Vertrauen in Personen durch Vertrauen in Regeln – nicht aus Zynismus, sondern aus epistemischer Bescheidenheit gegenüber menschlicher Fehlbarkeit.
Dieser Perspektivwechsel ist radikal. Er stellt nicht nur bestehende Geldsysteme infrage, sondern auch unsere politischen und institutionellen Grundlagen. Während klassische Systeme auf Hierarchien, Exklusivität und delegierter Macht beruhen, operiert Bitcoin auf Basis offener Teilhabe und individueller Verantwortung. Jeder Knoten ist autonom – aber keiner ist isoliert. Die Wahrheit, die sich im Netzwerk konstituiert, ist nicht das Produkt von Autorität, sondern das Ergebnis reproduzierbarer Verifikation. Nicht Glaube zählt, sondern Prüfung.
Konsens ist kein romantischer Idealzustand, sondern ein dynamischer Balanceakt. Er wird nicht durch Harmonie hergestellt, sondern durch Reibung, Konflikt und Iteration. Konsens in Bitcoin ist kein Konsens der Meinungen, sondern der Regeln. Und genau darin liegt seine Stabilität. Denn wo Meinungen divergieren, können Regeln konvergieren – vorausgesetzt, sie sind transparent, überprüfbar und konsequent angewandt.
Diese Logik verschiebt den Fokus von zentralisierter Macht zu verteilter Verantwortung. Bitcoin kennt keine exekutive Gewalt, keine privilegierten Klassen, keine Instanz, die im Namen aller spricht. Es kennt nur Regeln – und die freie Entscheidung, ihnen zu folgen oder nicht. Wer sich dem Konsens nicht anschließen will, kann abspalten. Forking ist keine Katastrophe, sondern ein systemimmanenter Ausdruck von Wahlfreiheit. In der Möglichkeit der Spaltung liegt die Stärke der Struktur.
Diese strukturelle Freiheit unterscheidet sich grundlegend vom klassischen, liberalen Freiheitsverständnis. Es geht nicht um die Willkür des Einzelnen, sondern um die Freiheit von willkürlicher Macht. Es ist kein Plädoyer für Individualismus, sondern für institutionelle Unabhängigkeit. Die Architektur selbst garantiert die Freiheit – nicht eine Instanz, die über sie wacht. In dieser Ethik ist Freiheit kein Ideal, sondern ein Designprinzip. Kein Zustand, sondern eine Infrastruktur.
Verantwortung entsteht nicht durch Appelle, sondern durch Transparenz. Jede Entscheidung, jede Transaktion, jeder Regelbruch ist öffentlich nachvollziehbar. Es gibt keine Geheimabsprachen, keine Privilegien, keine Ausnahmen. In dieser radikalen Offenheit liegt eine neue Form von Gerechtigkeit: nicht moralisch verordnet, sondern technisch ermöglicht. Gleichheit ist kein Ziel, sondern eine Eigenschaft des Systems selbst.
Bitcoin ist damit nicht nur ein technisches Protokoll, sondern ein Vorschlag für ein neues Modell gesellschaftlicher Ordnung. Eine Ordnung ohne Zentrum, aber nicht ohne Struktur. Eine Praxis der Wahrheit ohne Wahrheitsmonopol. Eine Gemeinschaft, die sich nicht über ideologische Übereinstimmung definiert, sondern über gemeinsame Regeln. Das politische Prinzip, das hier wirkt, ist die Zustimmung – nicht die Kontrolle.
In einer Zeit wachsender institutioneller Erosion, in der Vertrauen in klassische Strukturen schwindet, zeigt Bitcoin einen alternativen Weg: nicht zurück zur Vergangenheit, sondern nach vorn zu neuen Formen des Zusammenlebens. Es ist ein System, das sich nicht auf Versprechen verlässt, sondern auf Rechenbarkeit. Eine Ethik des Handelns, nicht des Glaubens. Eine Ordnung, die nicht durch Macht entsteht, sondern durch das Überflüssigmachen von Macht.
Bitcoin ist nicht perfekt. Aber es ist ehrlich in seiner Imperfektion. Es verspricht keine Utopie, sondern bietet ein robustes Werkzeug. Ein Werkzeug, das uns zwingt, über Macht, Wahrheit und Verantwortung neu nachzudenken. Es ist kein Ende, sondern ein Anfang – eine Einladung, eine neue politische Realität zu gestalten: nicht von oben diktiert, sondern von unten geschaffen.
-
 @ 04c915da:3dfbecc9
2025-05-20 15:50:22
@ 04c915da:3dfbecc9
2025-05-20 15:50:22There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ ec42c765:328c0600
2025-02-05 23:38:12
@ ec42c765:328c0600
2025-02-05 23:38:12カスタム絵文字とは
任意のオリジナル画像を絵文字のように文中に挿入できる機能です。
また、リアクション(Twitterの いいね のような機能)にもカスタム絵文字を使えます。

カスタム絵文字の対応状況(2025/02/06)

カスタム絵文字を使うためにはカスタム絵文字に対応したクライアントを使う必要があります。
※表は一例です。クライアントは他にもたくさんあります。
使っているクライアントが対応していない場合は、クライアントを変更する、対応するまで待つ、開発者に要望を送る(または自分で実装する)などしましょう。
対応クライアント
ここではnostterを使って説明していきます。
準備
カスタム絵文字を使うための準備です。
- Nostrエクステンション(NIP-07)を導入する
- 使いたいカスタム絵文字をリストに登録する
Nostrエクステンション(NIP-07)を導入する
Nostrエクステンションは使いたいカスタム絵文字を登録する時に必要になります。
また、環境(パソコン、iPhone、androidなど)によって導入方法が違います。
Nostrエクステンションを導入する端末は、実際にNostrを閲覧する端末と違っても構いません(リスト登録はPC、Nostr閲覧はiPhoneなど)。
Nostrエクステンション(NIP-07)の導入方法は以下のページを参照してください。
ログイン拡張機能 (NIP-07)を使ってみよう | Welcome to Nostr! ~ Nostrをはじめよう! ~
少し面倒ですが、これを導入しておくとNostr上の様々な場面で役立つのでより快適になります。
使いたいカスタム絵文字をリストに登録する
以下のサイトで行います。
右上のGet startedからNostrエクステンションでログインしてください。
例として以下のカスタム絵文字を導入してみます。
実際より絵文字が少なく表示されることがありますが、古い状態のデータを取得してしまっているためです。その場合はブラウザの更新ボタンを押してください。

- 右側のOptionsからBookmarkを選択

これでカスタム絵文字を使用するためのリストに登録できます。
カスタム絵文字を使用する
例としてブラウザから使えるクライアント nostter から使用してみます。
nostterにNostrエクステンションでログイン、もしくは秘密鍵を入れてログインしてください。
文章中に使用
- 投稿ボタンを押して投稿ウィンドウを表示
- 顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択
- : 記号に挟まれたアルファベットのショートコードとして挿入される

この状態で投稿するとカスタム絵文字として表示されます。
カスタム絵文字対応クライアントを使っている他ユーザーにもカスタム絵文字として表示されます。
対応していないクライアントの場合、ショートコードのまま表示されます。

ショートコードを直接入力することでカスタム絵文字の候補が表示されるのでそこから選択することもできます。

リアクションに使用
- 任意の投稿の顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択

カスタム絵文字リアクションを送ることができます。

カスタム絵文字を探す
先述したemojitoからカスタム絵文字を探せます。
例えば任意のユーザーのページ emojito ロクヨウ から探したり、 emojito Browse all からnostr全体で最近作成、更新された絵文字を見たりできます。
また、以下のリンクは日本語圏ユーザーが作ったカスタム絵文字を集めたリストです(2025/02/06)
※漏れがあるかもしれません
各絵文字セットにあるOpen in emojitoのリンクからemojitoに飛び、使用リストに追加できます。
以上です。
次:Nostrのカスタム絵文字の作り方
Yakihonneリンク Nostrのカスタム絵文字の作り方
Nostrリンク nostr:naddr1qqxnzdesxuunzv358ycrgveeqgswcsk8v4qck0deepdtluag3a9rh0jh2d0wh0w9g53qg8a9x2xqvqqrqsqqqa28r5psx3
仕様
-
 @ 04c915da:3dfbecc9
2025-05-20 15:47:16
@ 04c915da:3dfbecc9
2025-05-20 15:47:16Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ d9c98e71:37007462
2025-05-22 09:47:40
@ d9c98e71:37007462
2025-05-22 09:47:40-
Ein Kind schweigt nicht aus Höflichkeit. Es hört bloß Dinge, die Erwachsene längst verlernt haben zu hören.
-
Das System gibt dir einen Namen, damit du vergisst, wer du vorher warst.
-
Liebe ist nicht das Gegenteil von Angst. Sie ist nur deren zärtlichste Form.
-
Manche Wahrheiten tragen Masken – nicht, um zu lügen, sondern um nicht zerschlagen zu werden.
-
Ein Kind versteht die Welt nicht weniger. Es sieht sie nur ohne die Lügen, mit denen wir sie uns erklären.
-
Die Erinnerung ist ein Dieb, der sanft stiehlt und erst später das Gewicht seiner Beute offenbart.
-
Man flieht nicht vor dem Käfig. Man flieht vor dem eigenen Wunsch, darin bleiben zu dürfen.
-
Wo Worte enden, beginnt nicht die Stille, sondern das, was wir nicht zu denken wagen.
-
Ein System überlebt nicht durch Kontrolle, sondern durch den Glauben, es sei nötig.
-
Die Zeit heilt nichts. Sie deckt nur zu, was niemand mehr sehen will.
-
-
 @ ec42c765:328c0600
2025-02-05 23:16:35
@ ec42c765:328c0600
2025-02-05 23:16:35てすと
nostr:nevent1qqst3uqlls4yr9vys4dza2sgjle3ly37trck7jgdmtr23uuz52usjrqqqnjgr
nostr:nevent1qqsdvchy5d27zt3z05rr3q6vvmzgslslxwu0p4dfkvxwhmvxldn9djguvagp2
test
てs
-
 @ d9c98e71:37007462
2025-05-22 09:46:32
@ d9c98e71:37007462
2025-05-22 09:46:32„Die Zukunft kommt nicht von selbst. Sie wird still gebaut – Zeile für Zeile, Entscheidung für Entscheidung.“
– Ursprung vergessen, Wahrheit geblieben
Was, wenn all das – der Rückzug, das neue Geld, die Verantwortung, das Misstrauen – nicht Flucht ist, sondern Heimkehr? Nicht Ablehnung der Welt, sondern ihre bewusste Rekonstruktion? Was, wenn der wahre Bruch nicht darin liegt, ein anderes System zu benutzen, sondern darin, anders zu sein?
Die Technologie war nie das Ziel. Sie ist nur der Raum, in dem sich etwas Menschlicheres entfalten kann: Klarheit. Konsequenz. Verantwortung ohne Zwang. Vertrauen ohne Blindheit. Eigentum ohne Bedingungen. Was mit Code beginnt, endet mit einer Haltung.
Manche nennen es Exit. Andere Rebellion. Vielleicht ist es beides. Vielleicht ist es aber auch einfach der leise Moment, in dem jemand erkennt: Ich kann mich entscheiden. Und diese Entscheidung verändert nicht die Welt – aber sie verändert mich in ihr.
Die Freiheit, die hier entsteht, ist nicht laut. Nicht kollektiv. Nicht romantisch. Sie ist nüchtern, präzise, anspruchsvoll. Sie fordert Selbstprüfung statt Meinung, Handlung statt Haltung. Und sie zieht keine Grenzen zwischen Mensch und Werkzeug – sie zeigt nur, was möglich wird, wenn man bereit ist, weniger zu verlangen und mehr zu tragen.
Das neue Geld, das neue Netzwerk, die neue Kultur – sie leben nicht irgendwo da draußen. Sie entstehen dort, wo jemand beschließt, nicht mehr mitzuspielen – und auch nicht mehr zu kämpfen. Sondern einfach zu bauen. Still. Beharrlich. Unaufhaltsam.
-
 @ ec42c765:328c0600
2025-02-05 22:05:55
@ ec42c765:328c0600
2025-02-05 22:05:55カスタム絵文字とは
任意のオリジナル画像を絵文字のように文中に挿入できる機能です。
また、リアクション(Twitterの いいね のような機能)にもカスタム絵文字を使えます。

カスタム絵文字の対応状況(2025/02/06)

カスタム絵文字を使うためにはカスタム絵文字に対応したクライアントを使う必要があります。
※表は一例です。クライアントは他にもたくさんあります。
使っているクライアントが対応していない場合は、クライアントを変更する、対応するまで待つ、開発者に要望を送る(または自分で実装する)などしましょう。
対応クライアント
ここではnostterを使って説明していきます。
準備
カスタム絵文字を使うための準備です。
- Nostrエクステンション(NIP-07)を導入する
- 使いたいカスタム絵文字をリストに登録する
Nostrエクステンション(NIP-07)を導入する
Nostrエクステンションは使いたいカスタム絵文字を登録する時に必要になります。
また、環境(パソコン、iPhone、androidなど)によって導入方法が違います。
Nostrエクステンションを導入する端末は、実際にNostrを閲覧する端末と違っても構いません(リスト登録はPC、Nostr閲覧はiPhoneなど)。
Nostrエクステンション(NIP-07)の導入方法は以下のページを参照してください。
ログイン拡張機能 (NIP-07)を使ってみよう | Welcome to Nostr! ~ Nostrをはじめよう! ~
少し面倒ですが、これを導入しておくとNostr上の様々な場面で役立つのでより快適になります。
使いたいカスタム絵文字をリストに登録する
以下のサイトで行います。
右上のGet startedからNostrエクステンションでログインしてください。
例として以下のカスタム絵文字を導入してみます。
実際より絵文字が少なく表示されることがありますが、古い状態のデータを取得してしまっているためです。その場合はブラウザの更新ボタンを押してください。

- 右側のOptionsからBookmarkを選択

これでカスタム絵文字を使用するためのリストに登録できます。
カスタム絵文字を使用する
例としてブラウザから使えるクライアント nostter から使用してみます。
nostterにNostrエクステンションでログイン、もしくは秘密鍵を入れてログインしてください。
文章中に使用
- 投稿ボタンを押して投稿ウィンドウを表示
- 顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択
- : 記号に挟まれたアルファベットのショートコードとして挿入される

この状態で投稿するとカスタム絵文字として表示されます。
カスタム絵文字対応クライアントを使っている他ユーザーにもカスタム絵文字として表示されます。
対応していないクライアントの場合、ショートコードのまま表示されます。

ショートコードを直接入力することでカスタム絵文字の候補が表示されるのでそこから選択することもできます。

リアクションに使用
- 任意の投稿の顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択

カスタム絵文字リアクションを送ることができます。

カスタム絵文字を探す
先述したemojitoからカスタム絵文字を探せます。
例えば任意のユーザーのページ emojito ロクヨウ から探したり、 emojito Browse all からnostr全体で最近作成、更新された絵文字を見たりできます。
また、以下のリンクは日本語圏ユーザーが作ったカスタム絵文字を集めたリストです(2025/02/06)
※漏れがあるかもしれません
各絵文字セットにあるOpen in emojitoのリンクからemojitoに飛び、使用リストに追加できます。
以上です。
次:Nostrのカスタム絵文字の作り方
Yakihonneリンク Nostrのカスタム絵文字の作り方
Nostrリンク nostr:naddr1qqxnzdesxuunzv358ycrgveeqgswcsk8v4qck0deepdtluag3a9rh0jh2d0wh0w9g53qg8a9x2xqvqqrqsqqqa28r5psx3
仕様
-
 @ ec42c765:328c0600
2025-02-05 20:30:46
@ ec42c765:328c0600
2025-02-05 20:30:46カスタム絵文字とは
任意のオリジナル画像を絵文字のように文中に挿入できる機能です。
また、リアクション(Twitterの いいね のような機能)にもカスタム絵文字を使えます。

カスタム絵文字の対応状況(2024/02/05)

カスタム絵文字を使うためにはカスタム絵文字に対応したクライアントを使う必要があります。
※表は一例です。クライアントは他にもたくさんあります。
使っているクライアントが対応していない場合は、クライアントを変更する、対応するまで待つ、開発者に要望を送る(または自分で実装する)などしましょう。
対応クライアント
ここではnostterを使って説明していきます。
準備
カスタム絵文字を使うための準備です。
- Nostrエクステンション(NIP-07)を導入する
- 使いたいカスタム絵文字をリストに登録する
Nostrエクステンション(NIP-07)を導入する
Nostrエクステンションは使いたいカスタム絵文字を登録する時に必要になります。
また、環境(パソコン、iPhone、androidなど)によって導入方法が違います。
Nostrエクステンションを導入する端末は、実際にNostrを閲覧する端末と違っても構いません(リスト登録はPC、Nostr閲覧はiPhoneなど)。
Nostrエクステンション(NIP-07)の導入方法は以下のページを参照してください。
ログイン拡張機能 (NIP-07)を使ってみよう | Welcome to Nostr! ~ Nostrをはじめよう! ~
少し面倒ですが、これを導入しておくとNostr上の様々な場面で役立つのでより快適になります。
使いたいカスタム絵文字をリストに登録する
以下のサイトで行います。
右上のGet startedからNostrエクステンションでログインしてください。
例として以下のカスタム絵文字を導入してみます。
実際より絵文字が少なく表示されることがありますが、古い状態のデータを取得してしまっているためです。その場合はブラウザの更新ボタンを押してください。

- 右側のOptionsからBookmarkを選択

これでカスタム絵文字を使用するためのリストに登録できます。
カスタム絵文字を使用する
例としてブラウザから使えるクライアント nostter から使用してみます。
nostterにNostrエクステンションでログイン、もしくは秘密鍵を入れてログインしてください。
文章中に使用
- 投稿ボタンを押して投稿ウィンドウを表示
- 顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択
- : 記号に挟まれたアルファベットのショートコードとして挿入される

この状態で投稿するとカスタム絵文字として表示されます。
カスタム絵文字対応クライアントを使っている他ユーザーにもカスタム絵文字として表示されます。
対応していないクライアントの場合、ショートコードのまま表示されます。

ショートコードを直接入力することでカスタム絵文字の候補が表示されるのでそこから選択することもできます。

リアクションに使用
- 任意の投稿の顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択

カスタム絵文字リアクションを送ることができます。

カスタム絵文字を探す
先述したemojitoからカスタム絵文字を探せます。
例えば任意のユーザーのページ emojito ロクヨウ から探したり、 emojito Browse all からnostr全体で最近作成、更新された絵文字を見たりできます。
また、以下のリンクは日本語圏ユーザーが作ったカスタム絵文字を集めたリストです(2024/06/30)
※漏れがあるかもしれません
各絵文字セットにあるOpen in emojitoのリンクからemojitoに飛び、使用リストに追加できます。
以上です。
次:Nostrのカスタム絵文字の作り方
Yakihonneリンク Nostrのカスタム絵文字の作り方
Nostrリンク nostr:naddr1qqxnzdesxuunzv358ycrgveeqgswcsk8v4qck0deepdtluag3a9rh0jh2d0wh0w9g53qg8a9x2xqvqqrqsqqqa28r5psx3
仕様
-
 @ d9c98e71:37007462
2025-05-22 09:45:57
@ d9c98e71:37007462
2025-05-22 09:45:57-
Im Nichts gibt es keine Befreiung. Nur die Ernüchterung der Illusion.
-
Das System braucht dich mehr, als du es brauchst. Deshalb lügt es – liebevoll.
-
Die Stille singt ein Lied ohne Ton. Ein Chor der Leere, der dich umarmt, bis du dich selbst verlierst.
-
Familie ist das erste Gefängnis, das man liebt, bevor man weiß, was Freiheit bedeutet.
-
Die Familie gibt Halt und hält fest. Beides ist nicht immer dasselbe.
-
Die Zukunft ist ein Abgrund, der sich öffnet, um uns zu verschlingen. Und wir nennen es Fortschritt.
-
Die Schwermut ist der Ruf des Todes im Lebenden, ein dumpfer Widerhall des Willens.
-
Der Tod wartet nicht. Er erinnert an das, was wir nie gelebt haben.
-
Zwischen Eltern und Kindern liegt ein Ozean aus unausgesprochenen Wahrheiten.
-
Ein Kuss kann ein Versprechen sein – oder eine Lüge mit geschlossenem Mund.
-
-
 @ 3f770d65:7a745b24
2025-05-19 18:09:52
@ 3f770d65:7a745b24
2025-05-19 18:09:52🏌️ Monday, May 26 – Bitcoin Golf Championship & Kickoff Party
Location: Las Vegas, Nevada\ Event: 2nd Annual Bitcoin Golf Championship & Kick Off Party"\ Where: Bali Hai Golf Clubhouse, 5160 S Las Vegas Blvd, Las Vegas, NV 89119\ 🎟️ Get Tickets!
Details:
-
The week tees off in style with the Bitcoin Golf Championship. Swing clubs by day and swing to music by night.
-
Live performances from Nostr-powered acts courtesy of Tunestr, including Ainsley Costello and others.
-
Stop by the Purple Pill Booth hosted by Derek and Tanja, who will be on-boarding golfers and attendees to the decentralized social future with Nostr.
💬 May 27–29 – Bitcoin 2025 Conference at the Las Vegas Convention Center
Location: The Venetian Resort\ Main Attraction for Nostr Fans: The Nostr Lounge\ When: All day, Tuesday through Thursday\ Where: Right outside the Open Source Stage\ 🎟️ Get Tickets!
Come chill at the Nostr Lounge, your home base for all things decentralized social. With seating for \~50, comfy couches, high-tops, and good vibes, it’s the perfect space to meet developers, community leaders, and curious newcomers building the future of censorship-resistant communication.
Bonus: Right across the aisle, you’ll find Shopstr, a decentralized marketplace app built on Nostr. Stop by their booth to explore how peer-to-peer commerce works in a truly open ecosystem.
Daily Highlights at the Lounge:
-
☕️ Hang out casually or sit down for a deeper conversation about the Nostr protocol
-
🔧 1:1 demos from app teams
-
🛍️ Merch available onsite
-
🧠 Impromptu lightning talks
-
🎤 Scheduled Meetups (details below)
🎯 Nostr Lounge Meetups
Wednesday, May 28 @ 1:00 PM
- Damus Meetup: Come meet the team behind Damus, the OG Nostr app for iOS that helped kickstart the social revolution. They'll also be showcasing their new cross-platform app, Notedeck, designed for a more unified Nostr experience across devices. Grab some merch, get a demo, and connect directly with the developers.
Thursday, May 29 @ 1:00 PM
- Primal Meetup: Dive into Primal, the slickest Nostr experience available on web, Android, and iOS. With a built-in wallet, zapping your favorite creators and friends has never been easier. The team will be on-site for hands-on demos, Q\&A, merch giveaways, and deeper discussions on building the social layer of Bitcoin.
🎙️ Nostr Talks at Bitcoin 2025
If you want to hear from the minds building decentralized social, make sure you attend these two official conference sessions:
1. FROSTR Workshop: Multisig Nostr Signing
-
🕚 Time: 11:30 AM – 12:00 PM
-
📅 Date: Wednesday, May 28
-
📍 Location: Developer Zone
-
🎤 Speaker: nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqgdwaehxw309ahx7uewd3hkcqpqs9etjgzjglwlaxdhsveq0qksxyh6xpdpn8ajh69ruetrug957r3qf4ggfm (Austin Kelsay) @ Voltage\ A deep-dive into FROST-based multisig key management for Nostr. Geared toward devs and power users interested in key security.
2. Panel: Decentralizing Social Media
-
🕑 Time: 2:00 PM – 2:30 PM
-
📅 Date: Thursday, May 29
-
📍 Location: Genesis Stage
-
🎙️ Moderator: nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqy08wumn8ghj7mn0wd68yttjv4kxz7fwv3jhyettwfhhxuewd4jsqgxnqajr23msx5malhhcz8paa2t0r70gfjpyncsqx56ztyj2nyyvlq00heps - Bitcoin Strategy @ Roxom TV
-
👥 Speakers:
-
nostr:nprofile1qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcppemhxue69uhkummn9ekx7mp0qqsy2ga7trfetvd3j65m3jptqw9k39wtq2mg85xz2w542p5dhg06e5qmhlpep – Early Bitcoin dev, CEO @ Sirius Business Ltd
-
nostr:nprofile1qy2hwumn8ghj7mn0wd68ytndv9kxjm3wdahxcqg5waehxw309ahx7um5wfekzarkvyhxuet5qqsw4v882mfjhq9u63j08kzyhqzqxqc8tgf740p4nxnk9jdv02u37ncdhu7e3 – Analyst & Partner @ Ego Death Capital
Get the big-picture perspective on why decentralized social matters and how Nostr fits into the future of digital communication.
🌃 NOS VEGAS Meetup & Afterparty
Date: Wednesday, May 28\ Time: 7:00 PM – 1:00 AM\ Location: We All Scream Nightclub, 517 Fremont St., Las Vegas, NV 89101\ 🎟️ Get Tickets!
What to Expect:
-
🎶 Live Music Stage – Featuring Ainsley Costello, Sara Jade, Able James, Martin Groom, Bobby Shell, Jessie Lark, and other V4V artists
-
🪩 DJ Party Deck – With sets by nostr:nprofile1qy0hwumn8ghj7cmgdae82uewd45kketyd9kxwetj9e3k7mf6xs6rgqgcwaehxw309ahx7um5wgh85mm694ek2unk9ehhyecqyq7hpmq75krx2zsywntgtpz5yzwjyg2c7sreardcqmcp0m67xrnkwylzzk4 , nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqgkwaehxw309anx2etywvhxummnw3ezucnpdejqqg967faye3x6fxgnul77ej23l5aew8yj0x2e4a3tq2mkrgzrcvecfsk8xlu3 , and more DJs throwing down
-
🛰️ Live-streamed via Tunestr
-
🧠 Nostr Education – Talks by nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq37amnwvaz7tmwdaehgu3dwfjkccte9ejx2un9ddex7umn9ekk2tcqyqlhwrt96wnkf2w9edgr4cfruchvwkv26q6asdhz4qg08pm6w3djg3c8m4j , nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqg7waehxw309anx2etywvhxummnw3ezucnpdejz7ur0wp6kcctjqqspywh6ulgc0w3k6mwum97m7jkvtxh0lcjr77p9jtlc7f0d27wlxpslwvhau , nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq3vamnwvaz7tmwdaehgu3wd33xgetk9en82m30qqsgqke57uygxl0m8elstq26c4mq2erz3dvdtgxwswwvhdh0xcs04sc4u9p7d , nostr:nprofile1q9z8wumn8ghj7erzx3jkvmmzw4eny6tvw368wdt8da4kxamrdvek76mrwg6rwdngw94k67t3v36k77tev3kx7vn2xa5kjem9dp4hjepwd3hkxctvqyg8wumn8ghj7mn0wd68ytnhd9hx2qpqyaul8k059377u9lsu67de7y637w4jtgeuwcmh5n7788l6xnlnrgssuy4zk , nostr:nprofile1qy28wue69uhnzvpwxqhrqt33xgmn5dfsx5cqz9thwden5te0v4jx2m3wdehhxarj9ekxzmnyqqswavgevxe9gs43vwylumr7h656mu9vxmw4j6qkafc3nefphzpph8ssvcgf8 , and more.
-
🧾 Vendors & Project Booths – Explore new tools and services
-
🔐 Onboarding Stations – Learn how to use Nostr hands-on
-
🐦 Nostrich Flocking – Meet your favorite nyms IRL
-
🍸 Three Full Bars – Two floors of socializing overlooking vibrant Fremont Street
| | | | | ----------- | -------------------- | ------------------- | | Time | Name | Topic | | 7:30-7:50 | Derek | Nostr for Beginners | | 8:00-8:20 | Mark & Paul | Primal | | 8:30-8:50 | Terry | Damus | | 9:00-9:20 | OpenMike and Ainsley | V4V | | 09:30-09:50 | The Space | Space |
This is the after-party of the year for those who love freedom technology and decentralized social community. Don’t miss it.
Final Thoughts
Whether you're there to learn, network, party, or build, Bitcoin 2025 in Las Vegas has a packed week of Nostr-friendly programming. Be sure to catch all the events, visit the Nostr Lounge, and experience the growing decentralized social revolution.
🟣 Find us. Flock with us. Purple pill someone.
-
-
 @ 59cb0748:9602464b
2025-01-01 06:15:09
@ 59cb0748:9602464b
2025-01-01 06:15:09Nostrでお世話になっている方も、お世話になってない方も、こんにちは!
タコ頭大吉です!
NIP-23を使った初めての投稿です。
今回は、私がここ数ヶ月中にデザインをした三種類のビタキセケースの紹介記事になります!!
ビタキセを買ったもののあまり自分の好みに合う外観や仕様のケースがなく、いくつかプロトタイプを作りそれなりに時間をかけて考えたケース達です。
これら3シリーズに関しては、FDMタイプの3Dプリンタの精度、耐久性、出力後の作業性を考慮して一つのパーツで完結することに拘って設計をしました。
一定以上の充填率でプリントをすればそれなりに丈夫なはずです。
また、基本的に放熱性と保護性を両立できるように設計をしたつもります。
それぞれのモデルについて簡単に紹介をさせていただきますので、よろしければ各リポジトリに付属のREADMEを読んでいただいて自作、フィードバックをいただけましたら幸いです。
それでは、簡単に各モデルの紹介をさせていたきます。
AirLiftFrame
 最初に作ったモデルです!
少し大きいのが難点ですが、分厚めのフレームをベースとし基盤周辺をあえて囲わない設計により、保護性と放熱を阻害しない事の両立を狙っています。
最初に作ったモデルです!
少し大きいのが難点ですが、分厚めのフレームをベースとし基盤周辺をあえて囲わない設計により、保護性と放熱を阻害しない事の両立を狙っています。
TwinAirLiftFrame
 ビタキセを買い増ししたことにより、複数台をカッコよく運用したいという需要が自分の中に出てきたので、AirLiftFrameを2つくっつけたら良いのではと言うごくごく単純な発想でつくり始めたケースです。
しかし、ただ横並びにしただけでは廃熱が干渉するだけではなく、DCジャックやUSBポートへのアクセスが阻害されるという問題にすぐに気がつきました。
そこで、WebUI上でディスプレイの表示を上下反転出来ることに注目し、2台を上下逆向きに取り付ける事でそれらの問題を解決しました!
ビタキセを買い増ししたことにより、複数台をカッコよく運用したいという需要が自分の中に出てきたので、AirLiftFrameを2つくっつけたら良いのではと言うごくごく単純な発想でつくり始めたケースです。
しかし、ただ横並びにしただけでは廃熱が干渉するだけではなく、DCジャックやUSBポートへのアクセスが阻害されるという問題にすぐに気がつきました。
そこで、WebUI上でディスプレイの表示を上下反転出来ることに注目し、2台を上下逆向きに取り付ける事でそれらの問題を解決しました!
VoronoiShell
 AirLiftFrameシリーズのサイズを小型化する事から始めたプロジョクトです。
縦横の寸法の削減だけではなく、厚みを薄くつくリたいという希望がありました。
所が単純に薄くすると、持った時に発熱する背面パーツに手が触れてしまったり、落下などでぶつかった際に背面パーツが破損する懸念がありました。
そこで、(当初は付けたくはなかった)背面保護用のグリルをデザインする必要が出てきました。
初めは多角形でしたがあまりにもダサく、調べている内にVoronoi柄という有機的なパターンに行き付き即採用しました。
結果、ビタキセを取り付けると柄が見えなくなるのが勿体無いぐらい個性的でスタイリッシュなデザインに仕上がりました。
AirLiftFrameシリーズのサイズを小型化する事から始めたプロジョクトです。
縦横の寸法の削減だけではなく、厚みを薄くつくリたいという希望がありました。
所が単純に薄くすると、持った時に発熱する背面パーツに手が触れてしまったり、落下などでぶつかった際に背面パーツが破損する懸念がありました。
そこで、(当初は付けたくはなかった)背面保護用のグリルをデザインする必要が出てきました。
初めは多角形でしたがあまりにもダサく、調べている内にVoronoi柄という有機的なパターンに行き付き即採用しました。
結果、ビタキセを取り付けると柄が見えなくなるのが勿体無いぐらい個性的でスタイリッシュなデザインに仕上がりました。
いずれカスタム方法やインサートナットや増設ファンの選定方法等を紹介したいのですが、今回はNIP-23になれるという意図もあるので紹介に留めます! また、他の関連OSハードウェアプロジェクトのケースもデザインできたらと思っております!
今後ともタコ頭をよろしくお願いいたします。
-
 @ d9c98e71:37007462
2025-05-22 09:45:49
@ d9c98e71:37007462
2025-05-22 09:45:49-
Was man nicht selbst trägt, trägt einen am Ende zu Boden.
-
Erinnerungen sind Splitter eines Spiegels, der zerbrach. Sie schneiden dich, während du dein Gesicht in ihnen suchst.
-
Jede Berührung trägt den Abdruck der Vergänglichkeit. Selbst die zärtlichste ist nur ein Schatten.
-
Was ist die Grenze zwischen dem, was wir nennen, und dem, was wir nie sagen?
-
Fragen sind die Flügel eines Vogels, der nie den Himmel berührt.
-
Wir nennen es Familie. Aber manchmal ist es nur eine Geschichte, die keiner mehr zu Ende erzählen will.
-
Ein Kind, das fragt, bringt das System ins Wanken. Nicht durch die Antwort, sondern durch das Fragen selbst.
-
Je lauter die Behauptung, desto größer die Vorsicht.
-
Das Nichts ist der heimliche Gott, der im Zerfall des Seins thront.
-
Stille fließt durch uns, als wäre sie immer schon gewesen. Wir sind die Frage, die nie die Antwort findet.
-
-
 @ d9c98e71:37007462
2025-05-22 09:45:13
@ d9c98e71:37007462
2025-05-22 09:45:13„Vertrauen ist gut, Kontrolle ist besser – sagte die Macht.
Misstrauen ist gesund, Selbstverantwortung ist besser – sagte die Freiheit.“
– gehört im Rauschen, zwischen den Blöcken
Vertrauen ist die stille Grundlage jeder Gesellschaft. Doch es ist fragil. Es wird oft dort gefordert, wo es nicht verdient ist – in Systemen, die sich immun gemacht haben gegen Kontrolle, Konsequenz und Kritik. In solchen Strukturen ist Vertrauen keine Tugend mehr, sondern ein Werkzeug der Macht. Es wird benutzt, um Verantwortung abzugeben, um sich fügen zu müssen, um Teil eines Spiels zu sein, dessen Regeln man nicht mitbestimmen kann.
Misstrauen gilt oft als Schwäche. Doch es kann auch ein Zeichen von Reife sein. Es ist nicht Ablehnung, sondern Prüfung. Nicht Paranoia, sondern Wachsamkeit. Wer misstraut, schützt sich nicht nur vor Täuschung, sondern verteidigt das eigene Urteilsvermögen.
Ein System, das auf echtem Vertrauen beruhen will, muss bereit sein, Misstrauen auszuhalten. Es muss transparent, überprüfbar und austauschbar sein. Es darf Vertrauen nicht einfordern – es muss es verdienen. Vertrauen, das auf Kontrolle verzichtet, ist Glaube. Vertrauen, das auf überprüfbaren Regeln beruht, ist Klarheit.
In diesem Spannungsfeld steht das neue Geld. Es sagt: Vertraue nicht mir. Vertraue dem, was du selbst verifizieren kannst. Es ersetzt nicht Vertrauen durch Misstrauen, sondern durch Offenheit. Es fordert nichts – es bietet nur das, was es ist: ein System ohne Hintertüren, ohne Verwalter, ohne Privilegien.
Darin liegt seine Stärke. Es ist nicht darauf angewiesen, dass jemand daran glaubt. Es funktioniert, weil niemand es verändern kann. Es belohnt diejenigen, die prüfen. Und es enttäuscht jene, die hoffen, dass andere für sie denken.
Vertrauen ist eine Entscheidung. Misstrauen auch. Zwischen beiden steht Verantwortung – und wer bereit ist, sie zu tragen, wird keines von beiden mehr brauchen.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:51:54
@ 04c915da:3dfbecc9
2025-05-16 17:51:54In much of the world, it is incredibly difficult to access U.S. dollars. Local currencies are often poorly managed and riddled with corruption. Billions of people demand a more reliable alternative. While the dollar has its own issues of corruption and mismanagement, it is widely regarded as superior to the fiat currencies it competes with globally. As a result, Tether has found massive success providing low cost, low friction access to dollars. Tether claims 400 million total users, is on track to add 200 million more this year, processes 8.1 million transactions daily, and facilitates $29 billion in daily transfers. Furthermore, their estimates suggest nearly 40% of users rely on it as a savings tool rather than just a transactional currency.
Tether’s rise has made the company a financial juggernaut. Last year alone, Tether raked in over $13 billion in profit, with a lean team of less than 100 employees. Their business model is elegantly simple: hold U.S. Treasuries and collect the interest. With over $113 billion in Treasuries, Tether has turned a straightforward concept into a profit machine.
Tether’s success has resulted in many competitors eager to claim a piece of the pie. This has triggered a massive venture capital grift cycle in USD tokens, with countless projects vying to dethrone Tether. Due to Tether’s entrenched network effect, these challengers face an uphill battle with little realistic chance of success. Most educated participants in the space likely recognize this reality but seem content to perpetuate the grift, hoping to cash out by dumping their equity positions on unsuspecting buyers before they realize the reality of the situation.
Historically, Tether’s greatest vulnerability has been U.S. government intervention. For over a decade, the company operated offshore with few allies in the U.S. establishment, making it a major target for regulatory action. That dynamic has shifted recently and Tether has seized the opportunity. By actively courting U.S. government support, Tether has fortified their position. This strategic move will likely cement their status as the dominant USD token for years to come.
While undeniably a great tool for the millions of users that rely on it, Tether is not without flaws. As a centralized, trusted third party, it holds the power to freeze or seize funds at its discretion. Corporate mismanagement or deliberate malpractice could also lead to massive losses at scale. In their goal of mitigating regulatory risk, Tether has deepened ties with law enforcement, mirroring some of the concerns of potential central bank digital currencies. In practice, Tether operates as a corporate CBDC alternative, collaborating with authorities to surveil and seize funds. The company proudly touts partnerships with leading surveillance firms and its own data reveals cooperation in over 1,000 law enforcement cases, with more than $2.5 billion in funds frozen.
The global demand for Tether is undeniable and the company’s profitability reflects its unrivaled success. Tether is owned and operated by bitcoiners and will likely continue to push forward strategic goals that help the movement as a whole. Recent efforts to mitigate the threat of U.S. government enforcement will likely solidify their network effect and stifle meaningful adoption of rival USD tokens or CBDCs. Yet, for all their achievements, Tether is simply a worse form of money than bitcoin. Tether requires trust in a centralized entity, while bitcoin can be saved or spent without permission. Furthermore, Tether is tied to the value of the US Dollar which is designed to lose purchasing power over time, while bitcoin, as a truly scarce asset, is designed to increase in purchasing power with adoption. As people awaken to the risks of Tether’s control, and the benefits bitcoin provides, bitcoin adoption will likely surpass it.
-
 @ 04c915da:3dfbecc9
2025-05-15 15:31:45
@ 04c915da:3dfbecc9
2025-05-15 15:31:45Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ d9c98e71:37007462
2025-05-22 09:44:47
@ d9c98e71:37007462
2025-05-22 09:44:47-
Nähe ist gefährlich. Sie zeigt, wie weit entfernt wir wirklich voneinander sind.
-
Chaos braucht keine Form. Es genügt ihm, wenn du versuchst, ihm eine zu geben.
-
Die kindliche Fantasie ist Anarchie in Reinform. Rein, weil sie nicht gelernt hat, sich zu beugen.
-
Existenz ist ein Exil ohne Rückkehr. Wer liebt, liebt nur die Illusion eines Auswegs.
-
Zwischen den Zeilen flackert das Echo der Stille. Wer es hört, vergisst den Klang.
-
Wir leben in der Hoffnung, dass das Nichts uns nicht sieht. Doch es hat längst in uns Wohnung genommen.
-
Wir sterben nicht an der Zeit, sondern daran, dass wir glauben, sie gehöre uns.
-
Ein Kind lacht – und für einen Moment zittert die Ordnung.
-
Das Protokoll ist nicht moralisch. Es ist gerecht, weil es niemanden kennt.
-
Die Revolution beginnt nicht auf der Straße, sondern in dem Moment, in dem du aufhörst, dich selbst zu verraten.
-
-
 @ d9c98e71:37007462
2025-05-22 09:44:33
@ d9c98e71:37007462
2025-05-22 09:44:33-
Vertrauen stirbt nicht an Lügen, sondern am Schweigen dazwischen.
-
Freiheit ist ein Käfig aus offenen Türen. Du trittst hinaus und erstarrst in der Weite deiner eigenen Grenzen.
-
Nur wer sich selbst durchschaut, erkennt, ob die Liebe ihn überhaupt meint.
-
Ein Haus kann voller Menschen sein und doch leerer als ein verlassener Gedanke.
-
Die Krone der Zukunft liegt oft auf den Schultern derer, die nie gefragt wurden, ob sie das wollen.
-
Wahrer Reichtum ist nicht, was man besitzt, sondern was man niemandem schuldet.
-
Die Zeit ist ein Dieb, der Schatten stiehlt. Zurück bleibt ein Umriss, den niemand mehr füllt.
-
Die Trauer ist der Wundschrei des Seins über seinen eigenen Bruch.
-
Jede geordnete Welt ist ein Spiegelsaal. Und jeder Spiegel zerspringt am Schrei der Unangepassten.
-
Wir existieren wie Fußspuren im Staub eines verlassenen Raums – sichtbar nur für einen Moment.
-
-
 @ d9c98e71:37007462
2025-05-22 09:44:25
@ d9c98e71:37007462
2025-05-22 09:44:25„Sag mir, welches Geld du benutzt – und ich sage dir, an welche Welt du glaubst.“
– anonym, zirkulierend im digitalen Untergrund
Geld ist nie neutral. Es trägt eine Vorstellung davon in sich, was in einer Gesellschaft wertvoll ist – und wer entscheidet, was dieser Wert bedeutet. In den Währungen unserer Zeit steckt nicht nur Kaufkraft, sondern auch Gewalt. Unsichtbar, aber wirksam. Jede Inflation ist eine Umverteilung ohne Abstimmung. Jede Rettung durch Gelddrucken ein Eingriff in das Eigentum derer, die sparen. Jede staatliche Kontrolle über den Geldfluss ist auch Kontrolle über Leben.
Es ist leicht, Geld als bloßes Werkzeug zu sehen. Doch jedes Werkzeug formt auch seinen Nutzer. Wer Geld benutzt, das auf Schulden basiert, übernimmt unbewusst die Logik dieses Systems: Wachstum um jeden Preis, Gegenwart vor Zukunft, Kontrolle statt Vertrauen. Es ist kein Zufall, dass moralische Belohnung in dieser Welt selten mit finanzieller vergütet wird – weil das Geld selbst die Moral nicht kennt.
Die Frage ist nicht, ob Geld gut oder böse ist. Die Frage ist, ob es Verantwortung kennt. Ob es dem dient, der es hält, oder dem, der es kontrolliert. Ob es verlässlich ist – nicht nur in seiner Funktion, sondern auch in seiner Wirkung. Ein Geld, das jederzeit vermehrt werden kann, erlaubt jederzeit die Verschiebung von Lasten. Weg von den Verantwortlichen, hin zu den Stillen. Es belohnt die Nähe zur Quelle, nicht die Leistung. Es nährt den Zynismus.
Ein anderes Geld beginnt nicht bei der Technik, sondern bei der Ethik. Es fragt nicht: Was ist möglich? Sondern: Was ist richtig? Es basiert auf Knappheit – nicht um zu begrenzen, sondern um Ehrlichkeit zu erzwingen. Es kennt kein „Too Big to Fail“, kein Vertrauen auf Dekrete, keine moralische Grauzone. Wer es nutzt, steht in direkter Beziehung zu seinem Handeln – und kann sich nicht herausreden.
Vielleicht ist die wichtigste Wirkung dieses Geldes nicht wirtschaftlich, sondern moralisch: Es gibt dem Einzelnen die Möglichkeit, sauber zu wirtschaften, ohne Teil eines schmutzigen Spiels zu sein. Es ist kein Geld für jeden – sondern für jene, die bereit sind, wieder Verantwortung zu tragen. Nicht, weil sie müssen, sondern weil sie wollen.
-
 @ d9c98e71:37007462
2025-05-22 09:44:08
@ d9c98e71:37007462
2025-05-22 09:44:08-
Ein Vater, der schweigt, erzieht das Echo. Eine Mutter, die sich aufgibt, schenkt dem Nichts ein Gesicht.
-
Wer dem Nichts ins Auge sieht, braucht keine Autorität mehr.
-
Ein Augenblick – und schon ist er verloren. Wir wandern. Aber wohin?
-
Liebe beginnt nicht im Herzen, sondern im Zweifel. Sie wächst dort, wo man bleibt, obwohl man fliehen will.
-
Die Einsamkeit offenbart die Qual des Seienden – ein verlassenes Fragment des zersplitterten Willens.
-
Die Seele sammelt Splitter vergangener Welten. Doch keine Hand fügt sie je wieder zusammen.
-
Kinder fragen nicht nach Sinn. Sie leben ihn, bis man es ihnen austreibt.
-
Vertrauen ist eine Brücke aus Papier. Sie hält, solange keiner fragt, ob sie trägt.
-
Unsere Angst vor dem Nichts ist nur der Schrei des Ichs, das weiß, dass es niemals war.
-
Der Sinn entgleitet, je fester wir ihn fassen wollen – wie Nebel, der sich vor der Berührung auflöst.
-
-
 @ ec42c765:328c0600
2024-12-22 19:16:31
@ ec42c765:328c0600
2024-12-22 19:16:31この記事は前回の内容を把握している人向けに書いています(特にNostrエクステンション(NIP-07)導入)
手順
- 登録する画像を用意する
- 画像をweb上にアップロードする
- 絵文字セットに登録する
1. 登録する画像を用意する
以下のような方法で用意してください。
- 画像編集ソフト等を使って自分で作成する
- 絵文字作成サイトを使う(絵文字ジェネレーター、MEGAMOJI など)
- フリー画像を使う(いらすとや など)
データ量削減
Nostrでは画像をそのまま表示するクライアントが多いので、データ量が大きな画像をそのまま使うとモバイル通信時などに負担がかかります。
データ量を増やさないためにサイズやファイル形式を変更することをおすすめします。
以下は私のおすすめです。 * サイズ:正方形 128×128 ピクセル、長方形 任意の横幅×128 ピクセル * ファイル形式:webp形式(webp変換おすすめサイト toimg) * 単色、単純な画像の場合:png形式(webpにするとむしろサイズが大きくなる)
その他
- 背景透過画像
- ダークモード、ライトモード両方で見やすい色
がおすすめです。
2. 画像をweb上にアップロードする
よく分からなければ emojito からのアップロードで問題ないです。
普段使っている画像アップロード先があるならそれでも構いません。
気になる方はアップロード先を適宜選んでください。既に投稿されたカスタム絵文字の画像に対して
- 削除も差し替えもできない → emojito など
- 削除できるが差し替えはできない → Gyazo、nostrcheck.meなど
- 削除も差し替えもできる → GitHub 、セルフホスティングなど
これらは既にNostr上に投稿されたカスタム絵文字の画像を後から変更できるかどうかを指します。
どの方法でも新しく使われるカスタム絵文字を変更することは可能です。
同一のカスタム絵文字セットに同一のショートコードで別の画像を登録する形で対応できます。3. 絵文字セットに登録する
emojito から登録します。
右上のアイコン → + New emoji set から新規の絵文字セットを作成できます。


① 絵文字セット名を入力
基本的にカスタム絵文字はカスタム絵文字セットを作り、ひとまとまりにして登録します。
一度作った絵文字セットに後から絵文字を追加することもできます。
② 画像をアップロードまたは画像URLを入力
emojitoから画像をアップロードする場合、ファイル名に日本語などの2バイト文字が含まれているとアップロードがエラーになるようです。
その場合はファイル名を適当な英数字などに変更してください。
③ 絵文字のショートコードを入力
ショートコードは絵文字を呼び出す時に使用する場合があります。
他のカスタム絵文字と被っても問題ありませんが選択時に複数表示されて支障が出る可能性があります。
他と被りにくく長くなりすぎないショートコードが良いかもしれません。
ショートコードに使えるのは半角の英数字とアンダーバーのみです。
④ 追加
Add を押してもまだ作成完了にはなりません。

一度に絵文字を複数登録できます。
最後に右上の Save を押すと作成完了です。

画面が切り替わるので、右側の Options から Bookmark を選択するとそのカスタム絵文字セットを自分で使えるようになります。
既存の絵文字セットを編集するには Options から Edit を選択します。
以上です。
仕様
-
 @ d360efec:14907b5f
2025-05-13 00:39:56
@ d360efec:14907b5f
2025-05-13 00:39:56🚀📉 #BTC วิเคราะห์ H2! พุ่งชน 105K แล้วเจอแรงขาย... จับตา FVG 100.5K เป็นจุดวัดใจ! 👀📊
จากากรวิเคราะห์ทางเทคนิคสำหรับ #Bitcoin ในกรอบเวลา H2:
สัปดาห์ที่แล้ว #BTC ได้เบรคและพุ่งขึ้นอย่างแข็งแกร่งค่ะ 📈⚡ แต่เมื่อวันจันทร์ที่ผ่านมา ราคาได้ขึ้นไปชนแนวต้านบริเวณ 105,000 ดอลลาร์ แล้วเจอแรงขายย่อตัวลงมาตลอดทั้งวันค่ะ 🧱📉
ตอนนี้ ระดับที่น่าจับตาอย่างยิ่งคือโซน H4 FVG (Fair Value Gap ในกราฟ 4 ชั่วโมง) ที่ 100,500 ดอลลาร์ ค่ะ 🎯 (FVG คือโซนที่ราคาวิ่งผ่านไปเร็วๆ และมักเป็นบริเวณที่ราคามีโอกาสกลับมาทดสอบ/เติมเต็ม)
👇 โซน FVG ที่ 100.5K นี้ ยังคงเป็น Area of Interest ที่น่าสนใจสำหรับมองหาจังหวะ Long เพื่อลุ้นการขึ้นในคลื่นลูกถัดไปค่ะ!
🤔💡 อย่างไรก็ตาม การตัดสินใจเข้า Long หรือเทรดที่บริเวณนี้ ขึ้นอยู่กับว่าราคา แสดงปฏิกิริยาอย่างไรเมื่อมาถึงโซน 100.5K นี้ เพื่อยืนยันสัญญาณสำหรับการเคลื่อนไหวที่จะขึ้นสูงกว่าเดิมค่ะ!
เฝ้าดู Price Action ที่ระดับนี้อย่างใกล้ชิดนะคะ! 📍
BTC #Bitcoin #Crypto #คริปโต #TechnicalAnalysis #Trading #FVG #FairValueGap #PriceAction #MarketAnalysis #ลงทุนคริปโต #วิเคราะห์กราฟ #TradeSetup #ข่าวคริปโต #ตลาดคริปโต


-
 @ d9c98e71:37007462
2025-05-22 09:43:59
@ d9c98e71:37007462
2025-05-22 09:43:59-
Befreiung beginnt nicht mit einem Aufschrei. Sie beginnt mit einem leisen Nein.
-
Herkunft ist kein Zuhause. Es ist der Ort, an dem man lernt, warum man ging.
-
Manche Familien sind wie tote Götter. Man glaubt an sie, obwohl sie längst vergangen sind.
-
Wer das Nichts anschaut, sieht sich selbst – ein Schatten, der sich für Licht hält.
-
Das Schweigen des Universums ist keine Antwort. Es ist die endgültige Form der Gleichgültigkeit.
-
In der Dämmerung unserer Tage suchen wir die Sonne – eine Sonne, die nur noch in der Erinnerung brennt.
-
Freiheit beginnt, wenn man aufhört, sich retten zu lassen.
-
Wer nie verloren ging, hat sich selbst nie gesucht.
-
Gedanken zerfallen wie Tropfen, die nie den Boden erreichen.
-
Wahrheit ist selten laut. Sie flüstert – meist dann, wenn niemand mehr zuhört.
-
-
 @ d9c98e71:37007462
2025-05-22 09:43:51
@ d9c98e71:37007462
2025-05-22 09:43:51„Der Mensch ist frei geboren und überall liegt er in Ketten.“
– Jean-Jacques Rousseau
In einer Welt, die sich zunehmend durch technologische Umbrüche definiert, zeigt sich eine bemerkenswerte kognitive Dissonanz im Umgang mit neuen Paradigmen: Die Abwehr gegenüber Bitcoin ist selten eine Frage der Rationalität.
Häufig entsteht Ablehnung aus einer tief sitzenden Überforderung gegenüber dem Ungewohnten. Der Mensch meidet, was nicht in vertraute Erklärungsmuster passt – nicht aus Mangel an Intelligenz, sondern aus Gewohnheit.
So wirkt Bitcoin auf viele wie ein hermetisches System, dessen Mechanismen sich dem Alltagsverständnis entziehen. Dabei ist es, philosophisch betrachtet, der Fiat-Welt unter einem entscheidenden Aspekt überlegen: ihrer radikalen Transparenz.
Die Strukturen, welche das fiatbasierte Geldsystem tragen, sind in ihrer institutionellen Dichte kaum zu durchdringen. Zentralbanken, Aufsichtsbehörden, gesetzgeberische Rahmenwerke, geldpolitische Instrumente, Interbankenmärkte, internationale Regulierungsorgane – sie bilden einen verwaltungstechnischen Überbau, der in seiner Vielschichtigkeit eher einer mittelalterlichen Theologie als einem frei zugänglichen, rationalen System gleicht.
Das Vertrauen in diese Ordnung ist kein Produkt einer verstandesmäßigen Durchdringung, sondern das Ergebnis jahrzehntelanger Gewöhnung und autoritärer Setzung. Man glaubt an das Fiat-Geld, weil es da ist – nicht, weil man es versteht.
Bitcoin hingegen konfrontiert den Einzelnen mit der Notwendigkeit der Selbstverantwortung und fordert eine direkte Auseinandersetzung mit ihrer Funktionsweise: kryptografische Prinzipien, Dezentralität, Konsensmechanismen, digitale Knappheit. Dies wirkt zunächst sperrig, ja fast elitär. Doch diese Komplexität ist nicht strukturell intransparent, sondern technisch erklärbar, überprüfbar und – für jeden offen.
Während das Fiat-System in verschlossenen Räumen entscheidet, operiert Bitcoin auf einem offenen Protokoll. Die Ablehnung des Neuen beruht daher weniger auf seiner inhärenten Schwierigkeit als vielmehr auf einer anthropologischen Trägheit: Die Bequemlichkeit, sich von äußeren Instanzen verwalten zu lassen, wiegt schwerer als der Wunsch nach Souveränität.
Doch was ist wahrhaft komplex? Ist es nicht die blinde Akzeptanz eines Systems, dessen Grundlagen man niemals selbst prüfen kann? Ist es nicht der Glaube an eine Geldordnung, deren Stabilität von politischen Machtzentren abhängt?
Der Bitcoin hingegen stellt die radikale Frage: Was, wenn Vertrauen nicht mehr delegiert, sondern durch Code ersetzt werden kann? Was, wenn Verständlichkeit nicht aus Tradition, sondern aus Prinzipien entsteht?
In dieser Perspektive ist Bitcoin keine bloße technische Innovation, sondern ein philosophisches Statement: ein Plädoyer für epistemische Mündigkeit. Die vermeintliche Einfachheit des Alten ist in Wahrheit nur ein Schleier – und die gefühlte Schwierigkeit des Neuen ist der erste Schritt in die Freiheit.
-
 @ ec42c765:328c0600
2024-12-13 08:16:32
@ ec42c765:328c0600
2024-12-13 08:16:32Nostr Advent Calendar 2024 の 12日目の記事です。
昨日の 12/11 は きりの さんの 2024年のNostrリレー運営を振り返る でした。
nostr-zap-view 作った
リポジトリ: https://github.com/Lokuyow/nostr-zap-view/
動作確認ページ: https://lokuyow.github.io/nostr-zap-view/それ何?
特定の誰かや何かに宛てたZap(投げ銭)を一覧できるやつ
を
自分のWebサイトに設置できるやつ
自分のサイトに設置した例 * SNSリンク集ページ(最下部): https://lokuyow.github.io/
おいくらサッツ(Zap一覧ボタン): https://osats.money/
今日からビットコ(最下部): https://lokuyow.github.io/btc-dca-simulator/なんで作ったの?
私の去年のアドベントカレンダー
【Nostr】Webサイトにビットコインの投げ銭ボタンを設置しよう【Zap】
https://spotlight.soy/detail?article_id=ucd7cbrql/
が前提になってるけど長いので要約すると * ZapするやつはあるけどZap見るやつがないので欲しい * ZapをNostr(の典型的なkind:1クライアント)内だけに留めるのはもったいない * Webサイトの広告うざいからZap(的な何か)で置き換わって欲しいお前だれ?
非エンジニア、非プログラマー
AIにコード出させてるだけ人作った感想
できた
作った感想2
完成してから気付いた本当に作りたかったもの
こういうところにそのままZapを表示できる感じにしたい
 (ここまでちゃんとした商業ブログでなく)個人のブログやHPの端っこに「Sponsored by」欄があって名前が表示される感じ
(ここまでちゃんとした商業ブログでなく)個人のブログやHPの端っこに「Sponsored by」欄があって名前が表示される感じ
もうZapっていう文字もビットコインっていう文字もNostrも出さなくていいし説明もしなくていいのでは感がある
イメージはWebサイトを対象にしたニコニ広告 + スーパーチャット + 祭りとか神社の奉納者一覧
で思ったのは
個人からの投げ銭なら推し活的なものにしかならないけど
企業がNostrにアカウントを作ってサイトに投げ銭をしたら企業の広告になるんでは!?
~~企業がNostrにアカウントを!?デリヘルしか見たことない!~~今後
思いつき、予定は未定
* ボタン→ダイアログ形式でなくバナー、Embed形式にしてページアクセスですぐ見れるようにする * 多分リレーに負荷がかかるのでなんかする * Zapの文字は出さず「Sponsored by」等にする * 単純な最新順でなくする * 少額Zapをトリミング * 一定期間(一か月など)ごとで金額順にソート * 多分リレーに負荷がかかるのでなんかする * 今は投稿宛てのZapをWebサイト宛てのZapと勝手に言い張ってるだけなのでちゃんとWebサイト宛てのZapにする * NIPの提案が必要 * ウォレットの準拠も必要 * リレー(wss://~)宛てのZapもできてほしい将来
インターネットのすべてに投げ銭をさせろ
おわり
明日は mono さんの Open Sats 申請編 です!!
-
 @ d360efec:14907b5f
2025-05-12 04:01:23
@ d360efec:14907b5f
2025-05-12 04:01:23 -
 @ d9c98e71:37007462
2025-05-22 09:43:34
@ d9c98e71:37007462
2025-05-22 09:43:34„In Zeiten universeller Täuschung ist das Aussprechen der Wahrheit ein revolutionärer Akt.“
– George Orwell
Bitcoin ist nicht nur ein Werkzeug der ökonomischen Selbstermächtigung – er ist auch ein kulturelles Störsignal. Sein bloßes Funktionieren stellt die Legitimität des Bestehenden infrage. Eine Währung, die niemand ausgibt, niemand kontrolliert, niemand genehmigen muss, ist in ihrer bloßen Existenz eine stille Anklage gegen das, was als alternativlos gilt.
Es geht nicht nur um Technologie. Es geht um Haltung. Um das leise Beharren auf einem anderen Takt. In einer Welt, in der der Wert von oben definiert wird – durch Zentralbanken, Ratings, Verordnungen – bietet Bitcoin eine völlig andere Grundlage: Konsens, Knappheit, Mathematik. Kein politischer Willensakt, sondern ein physikalisches Versprechen.
Wer Bitcoin nutzt, trifft eine Entscheidung, die weit über Geld hinausgeht. Es ist die bewusste Verweigerung, Teil eines Systems zu sein, das auf Schulden basiert, auf Kontrolle, auf ständigem Zugriff. Es ist die Entscheidung, eine andere Art von Zukunft möglich zu machen – nicht durch Protest, sondern durch Praxis.
Diese Form der Dissidenz ist schwer zu greifen, weil sie sich nicht laut artikuliert. Sie baut keine Barrikaden, schreibt keine Manifeste, ruft nicht nach Aufmerksamkeit. Sie wählt den Rückzug als Methode. Die Abkopplung. Die schrittweise Reduktion von Abhängigkeiten.
Vielleicht ist das Revolutionäre an Bitcoin nicht der Konflikt, sondern die Abwesenheit davon. Kein Widerstand im klassischen Sinn, sondern eine Umleitung. Keine Konfrontation, sondern Konsequenz. Die leise Entscheidung, nicht mehr mitzuspielen – sondern etwas Besseres zu bauen.
Wer Bitcoin lebt, braucht keine Genehmigung. Keine Erklärung. Kein Spektakel. Nur einen Node. Eine Wallet. Ein wenig Disziplin. Und die Bereitschaft, Verantwortung zu tragen, wo andere noch Ansprüche stellen.
Es ist kein einfacher Weg. Aber es ist einer, den man gehen kann, ohne um Erlaubnis zu fragen.
-
 @ c9badfea:610f861a
2025-05-10 11:08:51
@ c9badfea:610f861a
2025-05-10 11:08:51- Install FUTO Keyboard (it's free and open source)
- Launch the app, tap Switch Input Methods and select FUTO Keyboard
- For voice input, choose FUTO Keyboard (needs mic permission) and grant permission While Using The App
- Configure keyboard layouts under Languages & Models as needed
Adding Support for Non-English Languages
Voice Input
- Download voice input models from the FUTO Keyboard Add-Ons page
- For languages like Chinese, German, Spanish, Russian, French, Portuguese, Korean, and Japanese, download the Multilingual-74 model
- For other languages, download Multilingual-244
- Open FUTO Keyboard, go to Languages & Models, and import the downloaded model under Voice Input
Dictionaries
- Get dictionary files from AOSP Dictionaries
- Open FUTO Keyboard, navigate to Languages & Models, and import the dictionary under Dictionary
ℹ️ When typing, tap the microphone icon to use voice input
-
 @ d9c98e71:37007462
2025-05-22 09:43:02
@ d9c98e71:37007462
2025-05-22 09:43:02„Was du besitzt, besitzt auch dich.“
– Henry David Thoreau
Bitcoin verändert nicht nur, wie wir Geld sehen, sondern auch, wie wir uns selbst sehen. Es stellt eine einfache Frage, die schwer wiegt: Wem traust du? Und tiefer noch: Bist du bereit, dir selbst zu trauen?
Selbstverwahrung ist kein technischer Akt – es ist eine innere Haltung. Wer seinen eigenen Schlüssel hält, muss sich nicht nur mit Tools, sondern mit sich selbst auseinandersetzen – mit Angst, Verantwortung und Freiheit. Die Gewissheit, dass niemand Zugriff hat, ist auch die Last, dass niemand rettet. Diese Form der Verantwortung ist für viele ungewohnt, fast schon beängstigend – in einer Welt, die absichert, verwaltet, entmündigt.
Bitcoin ist radikale Eigenverantwortung. Und genau das macht es zu einer psychologischen Schwelle. Es zwingt zur Selbsterkenntnis: Bin ich bereit, die Kontrolle wirklich zu übernehmen? Oder suche ich weiterhin nach Institutionen, nach Autoritäten, nach jemandem, der mir die Entscheidung abnimmt?
Spirituell betrachtet ist Bitcoin ein Spiegel. Es zeigt, woran wir glauben, was wir fürchten, worauf wir hoffen. In einer Welt voller Illusionen – über Wert, über Sicherheit, über Freiheit – ist Bitcoin brutal ehrlich. Es gibt nichts vor. Es bewertet nicht. Es funktioniert oder es funktioniert nicht. Und der Umgang damit offenbart viel über uns selbst.
Der Prozess, Bitcoin wirklich zu verstehen – nicht technisch, sondern existenziell – ist transformativ. Er entkoppelt unser Selbstwertgefühl von Zahlen auf Bankkonten. Er konfrontiert uns mit unserer Abhängigkeit von Bequemlichkeit. Er eröffnet die Möglichkeit, dass Freiheit nicht in äußeren Umständen liegt, sondern in einer inneren Haltung.
Für manche ist Bitcoin eine spirituelle Praxis – eine tägliche Übung in Geduld, Disziplin und Vertrauen. Nicht Vertrauen in andere, sondern in Prinzipien. In Mathematik. In Ursache und Wirkung. Bitcoin verzeiht keine Illusionen. Es bestraft Selbsttäuschung. Und gerade deshalb kann es ein Werkzeug sein – nicht nur der wirtschaftlichen, sondern auch der inneren Befreiung.
Wer sich darauf einlässt, begibt sich nicht nur auf einen neuen finanziellen Weg, sondern auf eine Reise zu sich selbst. Eine Reise, die nicht laut ist, nicht bequem, nicht sofort belohnend – aber ehrlich. Und vielleicht – heilsam.
-
 @ 7460b7fd:4fc4e74b
2025-05-21 02:35:36
@ 7460b7fd:4fc4e74b
2025-05-21 02:35:36如果比特币发明了真正的钱,那么 Crypto 是什么?
引言
比特币诞生之初就以“数字黄金”姿态示人,被支持者誉为人类历史上第一次发明了真正意义上的钱——一种不依赖国家信用、总量恒定且不可篡改的硬通货。然而十多年过去,比特币之后蓬勃而起的加密世界(Crypto)已经远超“货币”范畴:从智能合约平台到去中心组织,从去央行的稳定币到戏谑荒诞的迷因币,Crypto 演化出一个丰富而混沌的新生态。这不禁引发一个根本性的追问:如果说比特币解决了“真金白银”的问题,那么 Crypto 又完成了什么发明?
 Crypto 与政治的碰撞:随着Crypto版图扩张,全球政治势力也被裹挟进这场金融变革洪流(示意图)。比特币的出现重塑了货币信用,但Crypto所引发的却是一场更深刻的政治与治理结构实验。从华尔街到华盛顿,从散户论坛到主权国家,越来越多人意识到:Crypto不只是技术或金融现象,而是一种全新的政治表达结构正在萌芽。正如有激进论者所断言的:“比特币发明了真正的钱,而Crypto则在发明新的政治。”价格K线与流动性曲线,或许正成为这个时代社群意志和社会价值观的新型投射。
Crypto 与政治的碰撞:随着Crypto版图扩张,全球政治势力也被裹挟进这场金融变革洪流(示意图)。比特币的出现重塑了货币信用,但Crypto所引发的却是一场更深刻的政治与治理结构实验。从华尔街到华盛顿,从散户论坛到主权国家,越来越多人意识到:Crypto不只是技术或金融现象,而是一种全新的政治表达结构正在萌芽。正如有激进论者所断言的:“比特币发明了真正的钱,而Crypto则在发明新的政治。”价格K线与流动性曲线,或许正成为这个时代社群意志和社会价值观的新型投射。冲突结构:当价格挑战选票
传统政治中,选票是人民意志的载体,一人一票勾勒出民主治理的正统路径。而在链上的加密世界里,骤升骤降的价格曲线和真金白银的买卖行为却扮演起了选票的角色:资金流向成了民意走向,市场多空成为立场表决。价格行为取代选票,这听来匪夷所思,却已在Crypto社群中成为日常现实。每一次代币的抛售与追高,都是社区对项目决策的即时“投票”;每一根K线的涨跌,都折射出社区意志的赞同或抗议。市场行为本身承担了决策权与象征权——价格即政治,正在链上蔓延。
这一新生政治形式与旧世界的民主机制形成了鲜明冲突。bitcoin.org中本聪在比特币白皮书中提出“一CPU一票”的工作量证明共识,用算力投票取代了人为决策bitcoin.org。而今,Crypto更进一步,用资本市场的涨跌来取代传统政治的选举。支持某项目?直接购入其代币推高市值;反对某提案?用脚投票抛售资产。相比漫长的选举周期和层层代议制,链上市场提供了近乎实时的“公投”机制。但这种机制也引发巨大争议:资本的投票天然偏向持币多者(富者)的意志,是否意味着加密政治更为金权而非民权?持币多寡成为影响力大小,仿佛选举演变成了“一币一票”,巨鲸富豪俨然掌握更多话语权。这种与民主平等原则的冲突,成为Crypto政治形式饱受质疑的核心张力之一。
尽管如此,我们已经目睹市场投票在Crypto世界塑造秩序的威力:2016年以太坊因DAO事件分叉时,社区以真金白银“投票”决定了哪条链获得未来。arkhamintelligence.com结果是新链以太坊(ETH)成为主流,其市值一度超过2,800亿美元,而坚持原则的以太经典(ETC)市值不足35亿美元,不及前者的八十分之一arkhamintelligence.com。市场选择清楚地昭示了社区的政治意志。同样地,在比特币扩容之争、各类硬分叉博弈中,无不是由投资者和矿工用资金与算力投票,胜者存续败者黯然。价格成为裁决纷争的最终选票,冲击着传统“选票决胜”的政治理念。Crypto的价格民主,与现代代议民主正面相撞,激起当代政治哲思中前所未有的冲突火花。
治理与分配
XRP对决SEC成为了加密世界“治理与分配”冲突的经典战例。2020年底,美国证券交易委员会(SEC)突然起诉Ripple公司,指控其发行的XRP代币属于未注册证券,消息一出直接引爆市场恐慌。XRP价格应声暴跌,一度跌去超过60%,最低触及0.21美元coindesk.com。曾经位居市值前三的XRP险些被打入谷底,监管的强硬姿态似乎要将这个项目彻底扼杀。
然而XRP社区没有选择沉默。 大批长期持有者组成了自称“XRP军团”(XRP Army)的草根力量,在社交媒体上高调声援Ripple,对抗监管威胁。面对SEC的指控,他们集体发声,质疑政府选择性执法,声称以太坊当年发行却“逍遥法外”,只有Ripple遭到不公对待coindesk.com。正如《福布斯》的评论所言:没人预料到愤怒的加密散户投资者会掀起法律、政治和社交媒体领域的‘海啸式’反击,痛斥监管机构背弃了保护投资者的承诺crypto-law.us。这种草根抵抗监管的话语体系迅速形成:XRP持有者不但在网上掀起舆论风暴,还采取实际行动向SEC施压。他们发起了请愿,抨击SEC背离保护投资者初衷、诉讼给个人投资者带来巨大伤害,号召停止对Ripple的上诉纠缠——号称这是在捍卫全球加密用户的共同利益bitget.com。一场由民间主导的反监管运动就此拉开帷幕。
Ripple公司则选择背水一战,拒绝和解,在法庭上与SEC针锋相对地鏖战了近三年之久。Ripple坚称XRP并非证券,不应受到SEC管辖,即使面临沉重法律费用和业务压力也不妥协。2023年,这场持久战迎来了标志性转折:美国法庭作出初步裁决,认定XRP在二级市场的流通不构成证券coindesk.com。这一胜利犹如给沉寂已久的XRP注入强心针——消息公布当天XRP价格飙涨近一倍,盘中一度逼近1美元大关coindesk.com。沉重监管阴影下苟延残喘的项目,凭借司法层面的突破瞬间重获生机。这不仅是Ripple的胜利,更被支持者视为整个加密行业对SEC强权的一次胜仗。
XRP的对抗路线与某些“主动合规”的项目形成了鲜明对比。 稳定币USDC的发行方Circle、美国最大合规交易所Coinbase等选择了一条迎合监管的道路:它们高调拥抱现行法规,希望以合作换取生存空间。然而现实却给了它们沉重一击。USDC稳定币在监管风波中一度失去美元锚定,哪怕Circle及时披露储备状况也无法阻止恐慌蔓延,大批用户迅速失去信心,短时间内出现数十亿美元的赎回潮blockworks.co。Coinbase则更为直接:即便它早已注册上市、反复向监管示好,2023年仍被SEC指控为未注册证券交易所reuters.com,卷入漫长诉讼漩涡。可见,在迎合监管的策略下,这些机构非但未能换来监管青睐,反而因官司缠身或用户流失而丧失市场信任。 相比之下,XRP以对抗求生存的路线反而赢得了投资者的眼光:价格的涨跌成为社区投票的方式,抗争的勇气反过来强化了市场对它的信心。
同样引人深思的是另一种迥异的治理路径:技术至上的链上治理。 以MakerDAO为代表的去中心化治理模式曾被寄予厚望——MKR持币者投票决策、算法维持稳定币Dai的价值,被视为“代码即法律”的典范。然而,这套纯技术治理在市场层面却未能形成广泛认同,亦无法激发群体性的情绪动员。复杂晦涩的机制使得普通投资者难以参与其中,MakerDAO的治理讨论更多停留在极客圈子内部,在社会大众的政治对话中几乎听不见它的声音。相比XRP对抗监管所激发的铺天盖地关注,MakerDAO的治理实验显得默默无闻、难以“出圈”。这也说明,如果一种治理实践无法连接更广泛的利益诉求和情感共鸣,它在社会政治层面就难以形成影响力。
XRP之争的政治象征意义由此凸显: 它展示了一条“以市场对抗国家”的斗争路线,即通过代币价格的集体行动来回应监管权力的施压。在这场轰动业界的对决中,价格即是抗议的旗帜,涨跌映射着政治立场。XRP对SEC的胜利被视作加密世界向旧有权力宣告的一次胜利:资本市场的投票器可以撼动监管者的强权。这种“价格即政治”的张力,正是Crypto世界前所未有的社会实验:去中心化社区以市场行为直接对抗国家权力,在无形的价格曲线中凝聚起政治抗争的力量,向世人昭示加密货币不仅有技术和资本属性,更蕴含着不可小觑的社会能量和政治意涵。
不可归零的政治资本
Meme 币的本质并非廉价或易造,而在于其构建了一种“无法归零”的社群生存结构。 对于传统观点而言,多数 meme 币只是短命的投机游戏:价格暴涨暴跌后一地鸡毛,创始人套现跑路,投资者血本无归,然后“大家转去炒下一个”theguardian.com。然而,meme 币社群的独特之处在于——失败并不意味着终结,而更像是运动的逗号而非句号。一次币值崩盘后,持币的草根们往往并未散去;相反,他们汲取教训,准备东山再起。这种近乎“不死鸟”的循环,使得 meme 币运动呈现出一种数字政治循环的特质:价格可以归零,但社群的政治热情和组织势能不归零。正如研究者所指出的,加密领域中的骗局、崩盘等冲击并不会摧毁生态,反而成为让系统更加强韧的“健康应激”,令整个行业在动荡中变得更加反脆弱cointelegraph.com。对应到 meme 币,每一次暴跌和重挫,都是社群自我进化、卷土重来的契机。这个去中心化群体打造出一种自组织的安全垫,失败者得以在瓦砾上重建家园。对于草根社群、少数派乃至体制的“失败者”而言,meme 币提供了一个永不落幕的抗争舞台,一种真正反脆弱的政治性。正因如此,我们看到诸多曾被嘲笑的迷因项目屡败屡战:例如 Dogecoin 自2013年问世后历经八年沉浮,早已超越玩笑属性,成为互联网史上最具韧性的迷因之一frontiersin.org;支撑 Dogecoin 的正是背后强大的迷因文化和社区意志,它如同美国霸权支撑美元一样,为狗狗币提供了“永不中断”的生命力frontiersin.org。
“复活权”的数字政治意涵
这种“失败-重生”的循环结构蕴含着深刻的政治意涵:在传统政治和商业领域,一个政党选举失利或一家公司破产往往意味着清零出局,资源散尽、组织瓦解。然而在 meme 币的世界,社群拥有了一种前所未有的“复活权”。当项目崩盘,社区并不必然随之消亡,而是可以凭借剩余的人心和热情卷土重来——哪怕换一个 token 名称,哪怕重启一条链,运动依然延续。正如 Cheems 项目的核心开发者所言,在几乎无人问津、技术受阻的困境下,大多数人可能早已卷款走人,但 “CHEEMS 社区没有放弃,背景、技术、风投都不重要,重要的是永不言弃的精神”cointelegraph.com。这种精神使得Cheems项目起死回生,社区成员齐声宣告“我们都是 CHEEMS”,共同书写历史cointelegraph.com。与传统依赖风投和公司输血的项目不同,Cheems 完全依靠社区的信念与韧性存续发展,体现了去中心化运动的真谛cointelegraph.com。这意味着政治参与的门槛被大大降低:哪怕没有金主和官方背书,草根也能凭借群体意志赋予某个代币新的生命。对于身处社会边缘的群体来说,meme 币俨然成为自组织的安全垫和重新集结的工具。难怪有学者指出,近期涌入meme币浪潮的主力,正是那些对现实失望但渴望改变命运的年轻人theguardian.com——“迷茫的年轻人,想要一夜暴富”theguardian.com。meme币的炒作表面上看是投机赌博,但背后蕴含的是草根对既有金融秩序的不满与反抗:没有监管和护栏又如何?一次失败算不得什么,社区自有后路和新方案。这种由底层群众不断试错、纠错并重启的过程,本身就是一种数字时代的新型反抗运动和群众动员机制。
举例而言,Terra Luna 的沉浮充分展现了这种“复活机制”的政治力量。作为一度由风投资本热捧的项目,Luna 币在2022年的崩溃本可被视作“归零”的失败典范——稳定币UST瞬间失锚,Luna币价归零,数十亿美元灰飞烟灭。然而“崩盘”并没有画下休止符。Luna的残余社区拒绝承认失败命运,通过链上治理投票毅然启动新链,“复活”了 Luna 代币,再次回到市场交易reuters.com。正如 Terra 官方在崩盘后发布的推文所宣称:“我们力量永在社区,今日的决定正彰显了我们的韧性”reuters.com。事实上,原链更名为 Luna Classic 后,大批所谓“LUNC 军团”的散户依然死守阵地,誓言不离不弃;他们自发烧毁巨量代币以缩减供应、推动技术升级,试图让这个一度归零的项目重新燃起生命之火binance.com。失败者并未散场,而是化作一股草根洪流,奋力托举起项目的残迹。经过迷因化的叙事重塑,这场从废墟中重建价值的壮举,成为加密世界中草根政治的经典一幕。类似的案例不胜枚举:曾经被视为笑话的 DOGE(狗狗币)正因多年社群的凝聚而跻身主流币种,总市值一度高达数百亿美元,充分证明了“民有民享”的迷因货币同样可以笑傲市场frontiersin.org。再看最新的美国政治舞台,连总统特朗普也推出了自己的 meme 币 $TRUMP,号召粉丝拿真金白银来表达支持。该币首日即从7美元暴涨至75美元,两天后虽回落到40美元左右,但几乎同时,第一夫人 Melania 又发布了自己的 $Melania 币,甚至连就职典礼的牧师都跟风发行了纪念币theguardian.com!显然,对于狂热的群众来说,一个币的沉浮并非终点,而更像是运动的换挡——资本市场成为政治参与的新前线,你方唱罢我登场,meme 币的群众动员热度丝毫不减。值得注意的是,2024年出现的 Pump.fun 等平台更是进一步降低了这一循环的技术门槛,任何人都可以一键生成自己的 meme 币theguardian.com。这意味着哪怕某个项目归零,剩余的社区完全可以借助此类工具迅速复制一个新币接力,延续集体行动的火种。可以说,在 meme 币的世界里,草根社群获得了前所未有的再生能力和主动权,这正是一种数字时代的群众政治奇观:失败可以被当作梗来玩,破产能够变成重生的序章。
价格即政治:群众投机的新抗争
meme 币现象的兴盛表明:在加密时代,价格本身已成为一种政治表达。这些看似荒诞的迷因代币,将金融市场变成了群众宣泄情绪和诉求的另一个舞台。有学者将此概括为“将公民参与直接转化为了投机资产”cdn-brighterworld.humanities.mcmaster.ca——也就是说,社会运动的热情被注入币价涨跌,政治支持被铸造成可以交易的代币。meme 币融合了金融、技术与政治,通过病毒般的迷因文化激发公众参与,形成对现实政治的某种映射cdn-brighterworld.humanities.mcmaster.caosl.com。当一群草根投入全部热忱去炒作一枚毫无基本面支撑的币时,这本身就是一种大众政治动员的体现:币价暴涨,意味着一群人以戏谑的方式在向既有权威叫板;币价崩盘,也并不意味着信念的消亡,反而可能孕育下一次更汹涌的造势。正如有分析指出,政治类 meme 币的出现前所未有地将群众文化与政治情绪融入市场行情,价格曲线俨然成为民意和趋势的风向标cdn-brighterworld.humanities.mcmaster.ca。在这种局面下,投机不再仅仅是逐利,还是一种宣示立场、凝聚共识的过程——一次次看似荒唐的炒作背后,是草根对传统体制的不服与嘲讽,是失败者拒绝认输的呐喊。归根结底,meme 币所累积的,正是一种不可被归零的政治资本。价格涨落之间,群众的愤怒、幽默与希望尽显其中;这股力量不因一次挫败而消散,反而在市场的循环中愈发壮大。也正因如此,我们才说“价格即政治”——在迷因币的世界里,价格不只是数字,更是人民政治能量的晴雨表,哪怕归零也终将卷土重来。cdn-brighterworld.humanities.mcmaster.caosl.com
全球新兴现象:伊斯兰金融的入场
当Crypto在西方世界掀起市场治政的狂潮时,另一股独特力量也悄然融入这一场域:伊斯兰金融携其独特的道德秩序,开始在链上寻找存在感。长期以来,伊斯兰金融遵循着一套区别于世俗资本主义的原则:禁止利息(Riba)、反对过度投机(Gharar/Maysir)、强调实际资产支撑和道德投资。当这些原则遇上去中心化的加密技术,会碰撞出怎样的火花?出人意料的是,这两者竟在“以市场行为表达价值”这个层面产生了惊人的共鸣。伊斯兰金融并不拒绝市场机制本身,只是为其附加了道德准则;Crypto则将市场机制推向了政治高位,用价格来表达社群意志。二者看似理念迥异,实则都承认市场行为可以也应当承载社会价值观。这使得越来越多金融与政治分析人士开始关注:当虔诚的宗教伦理遇上狂野的加密市场,会塑造出何种新范式?
事实上,穆斯林世界已经在探索“清真加密”的道路。一些区块链项目致力于确保协议符合伊斯兰教法(Sharia)的要求。例如Haqq区块链发行的伊斯兰币(ISLM),从规则层面内置了宗教慈善义务——每发行新币即自动将10%拨入慈善DAO,用于公益捐赠,以符合天课(Zakat)的教义nasdaq.comnasdaq.com。同时,该链拒绝利息和赌博类应用,2022年还获得了宗教权威的教令(Fatwa)认可其合规性nasdaq.com。再看理念层面,伊斯兰经济学强调货币必须有内在价值、收益应来自真实劳动而非纯利息剥削。这一点与比特币的“工作量证明”精神不谋而合——有人甚至断言法定货币无锚印钞并不清真,而比特币这类需耗费能源生产的资产反而更符合教法初衷cointelegraph.com。由此,越来越多穆斯林投资者开始以道德投资的名义进入Crypto领域,将资金投向符合清真原则的代币和协议。
这种现象带来了微妙的双重合法性:一方面,Crypto世界原本奉行“价格即真理”的世俗逻辑,而伊斯兰金融为其注入了一股道德合法性,使部分加密资产同时获得了宗教与市场的双重背书;另一方面,即便在遵循宗教伦理的项目中,最终决定成败的依然是市场对其价值的认可。道德共识与市场共识在链上交汇,共同塑造出一种混合的新秩序。这一全球新兴现象引发广泛议论:有人将其视为金融民主化的极致表现——不同文化价值都能在市场平台上表达并竞争;也有人警惕这可能掩盖新的风险,因为把宗教情感融入高风险资产,既可能凝聚强大的忠诚度,也可能在泡沫破裂时引发信仰与财富的双重危机。但无论如何,伊斯兰金融的入场使Crypto的政治版图更加丰盈多元。从华尔街交易员到中东教士,不同背景的人们正通过Crypto这个奇特的舞台,对人类价值的表达方式进行前所未有的实验。
升华结语:价格即政治的新直觉
回顾比特币问世以来的这段历程,我们可以清晰地看到一条演进的主线:先有货币革命,后有政治发明。比特币赋予了人类一种真正自主的数字货币,而Crypto在此基础上完成的,则是一项前所未有的政治革新——它让市场价格行为承担起了类似政治选票的功能,开创了一种“价格即政治”的新直觉。在这个直觉下,市场不再只是冷冰冰的交易场所;每一次资本流动、每一轮行情涨落,都被赋予了社会意义和政治涵义。买入即表态,卖出即抗议,流动性的涌入或枯竭胜过千言万语的陈情。Crypto世界中,K线图俨然成为民意曲线,行情图就是政治晴雨表。决策不再由少数权力精英关起门来制定,而是在全球无眠的交易中由无数普通人共同谱写。这样的政治形式也许狂野,也许充满泡沫和噪音,但它不可否认地调动起了广泛的社会参与,让原本疏离政治进程的个体通过持币、交易重新找回了影响力的幻觉或实感。
“价格即政治”并非一句简单的口号,而是Crypto给予世界的全新想象力。它质疑了传统政治的正统性:如果一串代码和一群匿名投资者就能高效决策资源分配,我们为何还需要繁冗的官僚体系?它也拷问着自身的内在隐忧:当财富与权力深度绑定,Crypto政治如何避免堕入金钱统治的老路?或许,正是在这样的矛盾和张力中,人类政治的未来才会不断演化。Crypto所开启的,不仅是技术乌托邦或金融狂欢,更可能是一次对民主形式的深刻拓展和挑战。这里有最狂热的逐利者,也有最理想主义的社群塑梦者;有一夜暴富的神话,也有瞬间破灭的惨痛。而这一切汇聚成的洪流,正冲撞着工业时代以来既定的权力谱系。
当我们再次追问:Crypto究竟是什么? 或许可以这样回答——Crypto是比特币之后,人类完成的一次政治范式的试验性跃迁。在这里,价格行为化身为选票,资本市场演化为广场,代码与共识共同撰写“社会契约”。这是一场仍在进行的文明实验:它可能无声地融入既有秩序,也可能剧烈地重塑未来规则。但无论结局如何,如今我们已经见证:在比特币发明真正的货币之后,Crypto正在发明真正属于21世纪的政治。它以数字时代的语言宣告:在链上,价格即政治,市场即民意,代码即法律。这,或许就是Crypto带给我们的最直观而震撼的本质启示。
参考资料:
-
中本聪. 比特币白皮书: 一种点对点的电子现金系统. (2008)bitcoin.org
-
Arkham Intelligence. Ethereum vs Ethereum Classic: Understanding the Differences. (2023)arkhamintelligence.com
-
Binance Square (@渔神的加密日记). 狗狗币价格为何上涨?背后的原因你知道吗?binance.com
-
Cointelegraph中文. 特朗普的迷因币晚宴预期内容揭秘. (2025)cn.cointelegraph.com
-
慢雾科技 Web3Caff (@Lisa). 风险提醒:从 LIBRA 看“政治化”的加密货币骗局. (2025)web3caff.com
-
Nasdaq (@Anthony Clarke). How Cryptocurrency Aligns with the Principles of Islamic Finance. (2023)nasdaq.comnasdaq.com
-
Cointelegraph Magazine (@Andrew Fenton). DeFi can be halal but not DOGE? Decentralizing Islamic finance. (2023)cointelegraph.com
-
-
 @ 6bcc27d2:b67d296e
2024-10-21 03:54:32
@ 6bcc27d2:b67d296e
2024-10-21 03:54:32yugoです。 この記事は「Nostrasia2024 逆アドベントカレンダー」10/19の分です。Nostrasiaの当日はリアルタイムで配信を視聴していました。Nostrを使ってアプリケーションの再発明をすべきという発表を聴き、自分だったらどんなものを作ってみたいかを考えて少し調べたり試みたりしたのでその記録を書きます。また、超簡単なものですがおそらく世界初となるvisionOS対応のNostrクライアントをつくってみたので最後の方に紹介します。
アプリケーションを再発明する話があったのは、「What is Nostr Other Stuff?」と題したkaijiさんの発表でした。
Nostrプロトコルを使って既存のアプリケーションを再発明することで、ユーザ体験を損なわずにゆるやかな分散を促すことができ、プロトコルとしてのNostrも成長していくというような内容でした。
自分はまだNostrで何かをつくった経験はなかったので、実装に必要な仕様の知識がほとんどない状態からどのようなアプリケーションをつくってみたいかを考えました。
最初に思いついたのは、Scrapboxのようなネットワーク型のナレッジベースです。自分は最近visionOS勉強会をやっており、勉強会でナレッジを共有する手段としてScrapboxの導入を検討していました。
Nostrコミュニティにも有志によるScrapboxがありますが、Nostrクライアントがあればそれを使うだろうから同じくらいの実用性を備えたクライアントはまだ存在しないのではないかという見立てでした。
長文投稿やpublic chatなどの機能を組み合わせることで実現できるだろうか。そう思っていた矢先、NIP-54のWikiという規格があることを知りました。
https://github.com/nostr-protocol/nips/blob/master/54.md
まだちゃんとは読めていないですが、Scrapboxもwikiソフトウェアだし参考になりそうと思っています。正式な仕様に組み込まれていないようで、採用しているクライアントはfiatjafによるリファレンス実装(?)のwikistrくらいしか見つかりませんでした。
Scrapboxのようなナレッジベースを志向するNostrクライアントがあれば、後述するvisionOS対応クライアントの存在もありアカウントを使いまわせて嬉しいので試してみたいです。もし他にも似たようなサービスをどなたか知っていたら教えてください。
また現在は、勉強会やワークショップ、ハッカソンなどのコラボレーションワークを支援するためのツールを自分たちでも開発しています。Apple Vision Proに搭載されているvisionOSというプラットフォームで動作します。
https://image.nostr.build/14f0c1b8fbe5ce7754825c01b09280a4c22f87bbf3c2fa6d60dd724f98919c34.png
この画面で自分が入りたいスペースを選んで共有体験を開始します。
スライドなどのコンテンツや自らのアバターを同期させることで、遠隔地にいてもまるでオフラインかのように同じ空間を共有することが可能になります。
https://image.nostr.build/cfb75d3db2a9b9cd39f502d6426d5ef4f264b3d5d693b6fc9762735d2922b85c.jpg
ということなので、急遽visionOS対応のクライアントを作ってみました。検索しても1つも事例が出てこなかったので多分まだ世界で実装しているアプリはないのではないでしょうか。
とはいえ、クライアントを名乗っているもののまだ大した機能はなく、リレーからデータを取得するだけの読み取り専用です。
https://image.nostr.build/96e088cc6a082528682989ccc12b4312f9cb6277656e491578e32a0851ce50fe.png
画像では自分のプロフィールデータをリレーから取得しています。
まだどのライブラリもvisionOSに対応していなかったりで手こずったものの仕様の勉強になりました。
ただvisionOSアプリはiOSアプリ同様NIP-7が使えないので秘密鍵を自分で保管しなくてはならず、今後どう対処すべきかわかりかねています。これから時間ある時に少しずつ調べていこうと思っていますが、ネイティブアプリの秘密鍵周りはあまりリソースが多くないようにも感じました。もしどなたかその辺の実装に詳しい方いたら教えていただけると嬉しいです。
準備ができたらそのうちコードも公開したいと思っています。
これから少しずつ色んな機能を実装しながらNostrで遊んでいきたいです!
-
 @ 3bf0c63f:aefa459d
2024-09-06 12:49:46
@ 3bf0c63f:aefa459d
2024-09-06 12:49:46Nostr: a quick introduction, attempt #2
Nostr doesn't subscribe to any ideals of "free speech" as these belong to the realm of politics and assume a big powerful government that enforces a common ruleupon everybody else.
Nostr instead is much simpler, it simply says that servers are private property and establishes a generalized framework for people to connect to all these servers, creating a true free market in the process. In other words, Nostr is the public road that each market participant can use to build their own store or visit others and use their services.
(Of course a road is never truly public, in normal cases it's ran by the government, in this case it relies upon the previous existence of the internet with all its quirks and chaos plus a hand of government control, but none of that matters for this explanation).
More concretely speaking, Nostr is just a set of definitions of the formats of the data that can be passed between participants and their expected order, i.e. messages between clients (i.e. the program that runs on a user computer) and relays (i.e. the program that runs on a publicly accessible computer, a "server", generally with a domain-name associated) over a type of TCP connection (WebSocket) with cryptographic signatures. This is what is called a "protocol" in this context, and upon that simple base multiple kinds of sub-protocols can be added, like a protocol for "public-square style microblogging", "semi-closed group chat" or, I don't know, "recipe sharing and feedback".
-
 @ 51bbb15e:b77a2290
2025-05-21 00:24:36
@ 51bbb15e:b77a2290
2025-05-21 00:24:36Yeah, I’m sure everything in the file is legit. 👍 Let’s review the guard witness testimony…Oh wait, they weren’t at their posts despite 24/7 survellience instructions after another Epstein “suicide” attempt two weeks earlier. Well, at least the video of the suicide is in the file? Oh wait, a techical glitch. Damn those coincidences!
At this point, the Trump administration has zero credibility with me on anything related to the Epstein case and his clients. I still suspect the administration is using the Epstein files as leverage to keep a lot of RINOs in line, whereas they’d be sabotaging his agenda at every turn otherwise. However, I just don’t believe in ends-justify-the-means thinking. It’s led almost all of DC to toss out every bit of the values they might once have had.
-
 @ 4d2ae391:8ab9bc34
2025-05-22 09:30:53
@ 4d2ae391:8ab9bc34
2025-05-22 09:30:53Test
-
 @ d360efec:14907b5f
2025-05-10 03:57:17
@ d360efec:14907b5f
2025-05-10 03:57:17Disclaimer: * การวิเคราะห์นี้เป็นเพียงแนวทาง ไม่ใช่คำแนะนำในการซื้อขาย * การลงทุนมีความเสี่ยง ผู้ลงทุนควรตัดสินใจด้วยตนเอง
-
 @ 4d2ae391:8ab9bc34
2025-05-22 09:13:04
@ 4d2ae391:8ab9bc34
2025-05-22 09:13:04Test
-
 @ d9c98e71:37007462
2025-05-22 09:42:41
@ d9c98e71:37007462
2025-05-22 09:42:41„Anstatt das System zu bekämpfen, baue ein System, das es überflüssig macht.“
– zugeschrieben Buckminster Fuller
Die Gegenwart ist geprägt von Zentralisierung, digitaler Kontrolle und einem Finanzsystem, das Vertrauen verlangt, aber wenig zurückgibt. Für Bitcoiner stellt sich nicht mehr die Frage nach dem Ob, sondern nach dem Wie des Rückzugs aus diesem System.
Der klassische Goldstandard war Ausdruck eines strukturellen Misstrauens gegenüber staatlicher Willkür. Die Bindung des Geldes an ein rares Gut wie Gold disziplinierte die Geldpolitik – allerdings auf Kosten von Flexibilität, Zugänglichkeit und Dezentralität. Gold war zentral verwahrt, schwer zu transportieren und politisch angreifbar.
Bitcoin übernimmt die Idee der Begrenzung, ohne diese Schwächen: keine zentrale Verwahrung, leicht teilbar, digital übertragbar, resistent gegen Konfiszierung. Was beim Gold noch eine politische Vereinbarung war, ist bei Bitcoin eine technische Tatsache.
Anarchie wird oft missverstanden. Sie ist keine Ablehnung von Ordnung, sondern von Herrschaft. Sie setzt auf freiwillige Strukturen statt auf Zwang, auf Verantwortung statt auf Kontrolle. Bitcoin ist in diesem Sinne anarchisch. Es gibt keine zentrale Autorität, keine Intervention, kein Gatekeeping. Teilhabe ist offen, Regeln sind transparent, Entscheidungen beruhen auf Konsens. Es ist ein System, das sich jeder aneignen kann, ohne jemanden um Erlaubnis zu fragen.
Der Rückzug aus dem bestehenden System ist kein plötzlicher Bruch, sondern eine Praxis. Er beginnt mit Selbstverwahrung, der Vermeidung von KYC, der Nutzung von Peer-to-Peer-Technologien und dem bewussten Aufbau eigener Infrastruktur. Es geht nicht darum, das alte System zu stürzen, sondern es überflüssig zu machen – indem man es nicht mehr braucht.
Bitcoin ist keine Spekulation, kein Unternehmen, kein Produkt. Es ist eine Entscheidung. Eine Entscheidung für Autonomie. Für Verantwortung. Für Souveränität. Wer sich für diesen Weg entscheidet, wählt nicht die einfachste Lösung – sondern die ehrlichste. Der Preis ist Selbstverantwortung. Die Belohnung ist Freiheit.
Kein Spektakel. Keine Revolution. Nur ein Protokoll. Und ein Mensch, der es nutzt.
-
 @ c1e9ab3a:9cb56b43
2025-05-09 23:10:14
@ c1e9ab3a:9cb56b43
2025-05-09 23:10:14I. Historical Foundations of U.S. Monetary Architecture
The early monetary system of the United States was built atop inherited commodity money conventions from Europe’s maritime economies. Silver and gold coins—primarily Spanish pieces of eight, Dutch guilders, and other foreign specie—formed the basis of colonial commerce. These units were already integrated into international trade and piracy networks and functioned with natural compatibility across England, France, Spain, and Denmark. Lacking a centralized mint or formal currency, the U.S. adopted these forms de facto.
As security risks and the practical constraints of physical coinage mounted, banks emerged to warehouse specie and issue redeemable certificates. These certificates evolved into fiduciary media—claims on specie not actually in hand. Banks observed over time that substantial portions of reserves remained unclaimed for years. This enabled fractional reserve banking: issuing more claims than reserves held, so long as redemption demand stayed low. The practice was inherently unstable, prone to panics and bank runs, prompting eventual centralization through the formation of the Federal Reserve in 1913.
Following the Civil War and unstable reinstatements of gold convertibility, the U.S. sought global monetary stability. After World War II, the Bretton Woods system formalized the U.S. dollar as the global reserve currency. The dollar was nominally backed by gold, but most international dollars were held offshore and recycled into U.S. Treasuries. The Nixon Shock of 1971 eliminated the gold peg, converting the dollar into pure fiat. Yet offshore dollar demand remained, sustained by oil trade mandates and the unique role of Treasuries as global reserve assets.
II. The Structure of Fiduciary Media and Treasury Demand
Under this system, foreign trade surpluses with the U.S. generate excess dollars. These surplus dollars are parked in U.S. Treasuries, thereby recycling trade imbalances into U.S. fiscal liquidity. While technically loans to the U.S. government, these purchases act like interest-only transfers—governments receive yield, and the U.S. receives spendable liquidity without principal repayment due in the short term. Debt is perpetually rolled over, rarely extinguished.
This creates an illusion of global subsidy: U.S. deficits are financed via foreign capital inflows that, in practice, function more like financial tribute systems than conventional debt markets. The underlying asset—U.S. Treasury debt—functions as the base reserve asset of the dollar system, replacing gold in post-Bretton Woods monetary logic.
III. Emergence of Tether and the Parastatal Dollar
Tether (USDT), as a private issuer of dollar-denominated tokens, mimics key central bank behaviors while operating outside the regulatory perimeter. It mints tokens allegedly backed 1:1 by U.S. dollars or dollar-denominated securities (mostly Treasuries). These tokens circulate globally, often in jurisdictions with limited banking access, and increasingly serve as synthetic dollar substitutes.
If USDT gains dominance as the preferred medium of exchange—due to technological advantages, speed, programmability, or access—it displaces Federal Reserve Notes (FRNs) not through devaluation, but through functional obsolescence. Gresham’s Law inverts: good money (more liquid, programmable, globally transferable USDT) displaces bad (FRNs) even if both maintain a nominal 1:1 parity.
Over time, this preference translates to a systemic demand shift. Actors increasingly use Tether instead of FRNs, especially in global commerce, digital marketplaces, or decentralized finance. Tether tokens effectively become shadow base money.
IV. Interaction with Commercial Banking and Redemption Mechanics
Under traditional fractional reserve systems, commercial banks issue loans denominated in U.S. dollars, expanding the money supply. When borrowers repay loans, this destroys the created dollars and contracts monetary elasticity. If borrowers repay in USDT instead of FRNs:
- Banks receive a non-Fed liability (USDT).
- USDT is not recognized as reserve-eligible within the Federal Reserve System.
- Banks must either redeem USDT for FRNs, or demand par-value conversion from Tether to settle reserve requirements and balance their books.
This places redemption pressure on Tether and threatens its 1:1 peg under stress. If redemption latency, friction, or cost arises, USDT’s equivalence to FRNs is compromised. Conversely, if banks are permitted or compelled to hold USDT as reserve or regulatory capital, Tether becomes a de facto reserve issuer.
In this scenario, banks may begin demanding loans in USDT, mirroring borrower behavior. For this to occur sustainably, banks must secure Tether liquidity. This creates two options: - Purchase USDT from Tether or on the secondary market, collateralized by existing fiat. - Borrow USDT directly from Tether, using bank-issued debt as collateral.
The latter mirrors Federal Reserve discount window operations. Tether becomes a lender of first resort, providing monetary elasticity to the banking system by creating new tokens against promissory assets—exactly how central banks function.
V. Structural Consequences: Parallel Central Banking
If Tether begins lending to commercial banks, issuing tokens backed by bank notes or collateralized debt obligations: - Tether controls the expansion of broad money through credit issuance. - Its balance sheet mimics a central bank, with Treasuries and bank debt as assets and tokens as liabilities. - It intermediates between sovereign debt and global liquidity demand, replacing the Federal Reserve’s open market operations with its own issuance-redemption cycles.
Simultaneously, if Tether purchases U.S. Treasuries with FRNs received through token issuance, it: - Supplies the Treasury with new liquidity (via bond purchases). - Collects yield on government debt. - Issues a parallel form of U.S. dollars that never require redemption—an interest-only loan to the U.S. government from a non-sovereign entity.
In this context, Tether performs monetary functions of both a central bank and a sovereign wealth fund, without political accountability or regulatory transparency.
VI. Endgame: Institutional Inversion and Fed Redundancy
This paradigm represents an institutional inversion:
- The Federal Reserve becomes a legacy issuer.
- Tether becomes the operational base money provider in both retail and interbank contexts.
- Treasuries remain the foundational reserve asset, but access to them is mediated by a private intermediary.
- The dollar persists, but its issuer changes. The State becomes a fiscal agent of a decentralized financial ecosystem, not its monetary sovereign.
Unless the Federal Reserve reasserts control—either by absorbing Tether, outlawing its instruments, or integrating its tokens into the reserve framework—it risks becoming irrelevant in the daily function of money.
Tether, in this configuration, is no longer a derivative of the dollar—it is the dollar, just one level removed from sovereign control. The future of monetary sovereignty under such a regime is post-national and platform-mediated.
-
 @ 04c915da:3dfbecc9
2025-05-20 15:53:48
@ 04c915da:3dfbecc9
2025-05-20 15:53:48This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ 0176967e:1e6f471e
2024-07-28 15:31:13
@ 0176967e:1e6f471e
2024-07-28 15:31:13Objavte, ako avatari a pseudonymné identity ovplyvňujú riadenie kryptokomunít a decentralizovaných organizácií (DAOs). V tejto prednáške sa zameriame na praktické fungovanie decentralizovaného rozhodovania, vytváranie a správu avatarových profilov, a ich rolu v online reputačných systémoch. Naučíte sa, ako si vytvoriť efektívny pseudonymný profil, zapojiť sa do rôznych krypto projektov a využiť svoje aktivity na zarábanie kryptomien. Preskúmame aj príklady úspešných projektov a stratégie, ktoré vám pomôžu zorientovať sa a uspieť v dynamickom svete decentralizovaných komunít.
-
 @ d61f3bc5:0da6ef4a
2025-05-06 01:37:28
@ d61f3bc5:0da6ef4a
2025-05-06 01:37:28I remember the first gathering of Nostr devs two years ago in Costa Rica. We were all psyched because Nostr appeared to solve the problem of self-sovereign online identity and decentralized publishing. The protocol seemed well-suited for textual content, but it wasn't really designed to handle binary files, like images or video.
The Problem
When I publish a note that contains an image link, the note itself is resilient thanks to Nostr, but if the hosting service disappears or takes my image down, my note will be broken forever. We need a way to publish binary data without relying on a single hosting provider.
We were discussing how there really was no reliable solution to this problem even outside of Nostr. Peer-to-peer attempts like IPFS simply didn't work; they were hopelessly slow and unreliable in practice. Torrents worked for popular files like movies, but couldn't be relied on for general file hosting.
Awesome Blossom
A year later, I attended the Sovereign Engineering demo day in Madeira, organized by Pablo and Gigi. Many projects were presented over a three hour demo session that day, but one really stood out for me.
Introduced by hzrd149 and Stu Bowman, Blossom blew my mind because it showed how we can solve complex problems easily by simply relying on the fact that Nostr exists. Having an open user directory, with the corresponding social graph and web of trust is an incredible building block.
Since we can easily look up any user on Nostr and read their profile metadata, we can just get them to simply tell us where their files are stored. This, combined with hash-based addressing (borrowed from IPFS), is all we need to solve our problem.
How Blossom Works
The Blossom protocol (Blobs Stored Simply on Mediaservers) is formally defined in a series of BUDs (Blossom Upgrade Documents). Yes, Blossom is the most well-branded protocol in the history of protocols. Feel free to refer to the spec for details, but I will provide a high level explanation here.
The main idea behind Blossom can be summarized in three points:
- Users specify which media server(s) they use via their public Blossom settings published on Nostr;
- All files are uniquely addressable via hashes;
- If an app fails to load a file from the original URL, it simply goes to get it from the server(s) specified in the user's Blossom settings.
Just like Nostr itself, the Blossom protocol is dead-simple and it works!
Let's use this image as an example:
 If you look at the URL for this image, you will notice that it looks like this:
If you look at the URL for this image, you will notice that it looks like this:blossom.primal.net/c1aa63f983a44185d039092912bfb7f33adcf63ed3cae371ebe6905da5f688d0.jpgAll Blossom URLs follow this format:
[server]/[file-hash].[extension]The file hash is important because it uniquely identifies the file in question. Apps can use it to verify that the file they received is exactly the file they requested. It also gives us the ability to reliably get the same file from a different server.
Nostr users declare which media server(s) they use by publishing their Blossom settings. If I store my files on Server A, and they get removed, I can simply upload them to Server B, update my public Blossom settings, and all Blossom-capable apps will be able to find them at the new location. All my existing notes will continue to display media content without any issues.
Blossom Mirroring
Let's face it, re-uploading files to another server after they got removed from the original server is not the best user experience. Most people wouldn't have the backups of all the files, and/or the desire to do this work.
This is where Blossom's mirroring feature comes handy. In addition to the primary media server, a Blossom user can set one one or more mirror servers. Under this setup, every time a file is uploaded to the primary server the Nostr app issues a mirror request to the primary server, directing it to copy the file to all the specified mirrors. This way there is always a copy of all content on multiple servers and in case the primary becomes unavailable, Blossom-capable apps will automatically start loading from the mirror.
Mirrors are really easy to setup (you can do it in two clicks in Primal) and this arrangement ensures robust media handling without any central points of failure. Note that you can use professional media hosting services side by side with self-hosted backup servers that anyone can run at home.
Using Blossom Within Primal
Blossom is natively integrated into the entire Primal stack and enabled by default. If you are using Primal 2.2 or later, you don't need to do anything to enable Blossom, all your media uploads are blossoming already.
To enhance user privacy, all Primal apps use the "/media" endpoint per BUD-05, which strips all metadata from uploaded files before they are saved and optionally mirrored to other Blossom servers, per user settings. You can use any Blossom server as your primary media server in Primal, as well as setup any number of mirrors:
 ## Conclusion
## ConclusionFor such a simple protocol, Blossom gives us three major benefits:
- Verifiable authenticity. All Nostr notes are always signed by the note author. With Blossom, the signed note includes a unique hash for each referenced media file, making it impossible to falsify.
- File hosting redundancy. Having multiple live copies of referenced media files (via Blossom mirroring) greatly increases the resiliency of media content published on Nostr.
- Censorship resistance. Blossom enables us to seamlessly switch media hosting providers in case of censorship.
Thanks for reading; and enjoy! 🌸
-
 @ 0176967e:1e6f471e
2024-07-28 09:16:10
@ 0176967e:1e6f471e
2024-07-28 09:16:10Jan Kolčák pochádza zo stredného Slovenska a vystupuje pod umeleckým menom Deepologic. Hudbe sa venuje už viac než 10 rokov. Začínal ako DJ, ktorý s obľubou mixoval klubovú hudbu v štýloch deep-tech a afrohouse. Stále ho ťahalo tvoriť vlastnú hudbu, a preto sa začal vzdelávať v oblasti tvorby elektronickej hudby. Nakoniec vydal svoje prvé EP s názvom "Rezonancie". Učenie je pre neho celoživotný proces, a preto sa neustále zdokonaľuje v oblasti zvuku a kompozície, aby jeho skladby boli kvalitné na posluch aj v klube.
V roku 2023 si založil vlastnú značku EarsDeep Records, kde dáva príležitosť začínajúcim producentom. Jeho značku podporujú aj etablované mená slovenskej alternatívnej elektronickej scény. Jeho prioritou je sloboda a neškatulkovanie. Ako sa hovorí v jednej klasickej deephouseovej skladbe: "We are all equal in the house of deep." So slobodou ide ruka v ruke aj láska k novým technológiám, Bitcoinu a schopnosť udržať si v digitálnom svete prehľad, odstup a anonymitu.
V súčasnosti ďalej produkuje vlastnú hudbu, venuje sa DJingu a vedie podcast, kde zverejňuje svoje mixované sety. Na Lunarpunk festivale bude hrať DJ set tvorený vlastnou produkciou, ale aj skladby, ktoré sú blízke jeho srdcu.
Podcast Bandcamp Punk Nostr website alebo nprofile1qythwumn8ghj7un9d3shjtnwdaehgu3wvfskuep0qy88wumn8ghj7mn0wvhxcmmv9uq3xamnwvaz7tmsw4e8qmr9wpskwtn9wvhsz9thwden5te0wfjkccte9ejxzmt4wvhxjme0qyg8wumn8ghj7mn0wd68ytnddakj7qghwaehxw309aex2mrp0yh8qunfd4skctnwv46z7qpqguvns4ld8k2f3sugel055w7eq8zeewq7mp6w2stpnt6j75z60z3swy7h05
-
 @ d9c98e71:37007462
2025-05-22 09:07:42
@ d9c98e71:37007462
2025-05-22 09:07:42-
Melancholie ist die sanfteste Form der Rebellion. Ein Nein, das sich in Schönheit kleidet, um nicht verbrannt zu werden.
-
Die Menschheit sucht nach Erlösung und nennt das Kind dabei „Zukunft“, ohne zu merken, wie schwer diese Krone wiegt.
-
Nähe ohne Ehrlichkeit ist nur ein getarnter Abstand.
-
Jede Zentralisierung ist ein Denkfehler, der Macht als Fürsorge tarnt.
-
Sehnsucht ist ein Fluss, der rückwärts fließt. Du watest hinein, doch das Ufer zieht sich fort, unerreichbar fern.
-
Die letzte Form der Sklaverei ist die freiwillige Abhängigkeit.
-
Ein Kind spielt nicht, um zu vergessen. Es spielt, weil es noch nicht gelernt hat zu verdrängen.
-
Freiheit ist die Fähigkeit, in Ketten zu tanzen.
-
Das Leben ist der Widerhall eines sterbenden Willens. Nur im Nichts finden wir Erlösung.
-
Wer Kinder erzieht, erzieht auch seine Schatten. Sie kommen zurück, wenn das Haus still ist.
-
-
 @ c9badfea:610f861a
2025-05-06 00:36:40
@ c9badfea:610f861a
2025-05-06 00:36:40- Install Image Toolbox (it's free and open source)
- Open the app, then go to the Tools tab
- Select Checksum Tools
- Navigate to the Compare tab
- Choose the SHA-256 algorithm
- Pick the file to verify
- Enter the expected hash into the Checksum To Compare field
- A "Match!" message confirms successful verification
-
 @ 662f9bff:8960f6b2
2025-05-22 07:36:58
@ 662f9bff:8960f6b2
2025-05-22 07:36:58This past week I have been very busy in Holywood - just outside Belfast, Northern Ireland with a lot to do on top of my day-job! It was an unplanned trip but mission accomplished and we are off on the road again. I am writing this on my 3h30 Ryanair flight - so even in weeks like this you can find time to reflect quietly and think clearly if you look for it and seize the opportunity.
You might have noticed that I have "rebranded" the website and newsletter as "Letter From ...around the world". This reflects the reality that Hong Kong is not currently the "Asia World City" and I am not there. Whether it will ever reclaim that title again and when, or even if I can return remains to be seen. I am deeply saddened that after living 10 fabulous years in HK we had to abandon everything that Saturday night at the end of February.
This is the third time in my life that I have chosen Exit from "Loyalty, Voice or Exit" - (recall issue 09 - On Location).... Expect both Voice and Exit to become increasingly difficult or even unavailable in many jurisdictions. It is time to wake up. Talk to me if you are awake or curious!
One thing I learned back in 2004 on my first businss trip to New York is that "The way you react to a situation determines how you feel about it". This is one of so many insights that I learned from "The 7 Habits of Highly Effective People" by Steven Covey. I found the book at 4pm in the afternoon walking around outside my hotel trying to stay up to overcome jet-lag. I got back to the hotel and proceeded to devour the entire book overnight. I had never done that with any book before and I do not think I have done it since. Look out for a full review in an upcoming newsletter.
Thanks to Ali Abdaal for his passionate and insightful review of "Show Your Work" by Austin Kleon - clearly this is something that he has internalised and he does practice what he preaches. Indeed this is a short and easy read with many pictures and simple suggestions - recommended! I did read it on my Kindle and I am enjoying how the highlights automagically sync into Obsidian (see last week's find).
I was also inspired by Ali's How to Start a Youtube Channel explainer. I have been following Ali for about 5 years since he was a student doing these videos in his student room on his iPhone while studying Medicine in Cambridge. His passion for sharing his insights on how to study effectively as well as facilitating the learning that medical students needed to do enabled him to set up his own businesss. This set him on the road to his current 3 million subscribers and a business employing over a dozen people inspiring and helping others to acquire skills that are increasingly valuable in the the world today and going forward.
Over the coming months I will be experimenting with different channels and different media not only to discover new insights for myself but also to share things that I distill and find interesting. Also somewhat loosely inspired by "How to Get What you want and Want What You Have" by Jon Gray, I do recognize that I am now in the latter of the "Ten Time Periods" - if I had to pick one, I would say number 8 - at least that is how I feel!
So do subscribe to the newsletter and do follow along on Youtube. I'm obviously still in stage 1 of Ali's 3-stage process - so be patient and do give feedback, questions and suggestions!
Another day - another Airport...

That's it!
No one can be told what The Matrix is.\ You have to see it for yourself.**
Do share this newsletter with any of your friends and family who might be interested.
You can also email me at: LetterFrom@rogerprice.me
💡Enjoy the newsletters in your own language : Dutch, French, German, Serbian, Chinese Traditional & Simplified, Thai and Burmese.
-
 @ 2b24a1fa:17750f64
2025-05-22 08:18:28
@ 2b24a1fa:17750f64
2025-05-22 08:18:28Es ist pure Freiheit, Geschwindigkeit durch die eigene Kraft oder Bergab-Beschleunigung zu spüren. Kein störendes Motorengeräusch, das auch noch das ökologische Gewissen aufruft. Einfach nur Sein, an der Luft, im Wind. Wenn da doch nur … keine Ampel wäre.
Hören Sie den Beitrag „Ja oder ja – Begegnung mit der Staatsmacht, von Isa Mitza.
https://soundcloud.com/radiomuenchen/ja-oder-ja-begegnung-mit-der-staatsmacht-von-isa-mitza?
-
 @ 04c915da:3dfbecc9
2025-05-20 15:50:48
@ 04c915da:3dfbecc9
2025-05-20 15:50:48For years American bitcoin miners have argued for more efficient and free energy markets. It benefits everyone if our energy infrastructure is as efficient and robust as possible. Unfortunately, broken incentives have led to increased regulation throughout the sector, incentivizing less efficient energy sources such as solar and wind at the detriment of more efficient alternatives.
The result has been less reliable energy infrastructure for all Americans and increased energy costs across the board. This naturally has a direct impact on bitcoin miners: increased energy costs make them less competitive globally.
Bitcoin mining represents a global energy market that does not require permission to participate. Anyone can plug a mining computer into power and internet to get paid the current dynamic market price for their work in bitcoin. Using cellphone or satellite internet, these mines can be located anywhere in the world, sourcing the cheapest power available.
Absent of regulation, bitcoin mining naturally incentivizes the build out of highly efficient and robust energy infrastructure. Unfortunately that world does not exist and burdensome regulations remain the biggest threat for US based mining businesses. Jurisdictional arbitrage gives miners the option of moving to a friendlier country but that naturally comes with its own costs.
Enter AI. With the rapid development and release of AI tools comes the requirement of running massive datacenters for their models. Major tech companies are scrambling to secure machines, rack space, and cheap energy to run full suites of AI enabled tools and services. The most valuable and powerful tech companies in America have stumbled into an accidental alliance with bitcoin miners: THE NEED FOR CHEAP AND RELIABLE ENERGY.
Our government is corrupt. Money talks. These companies will push for energy freedom and it will greatly benefit us all.
-
 @ 0176967e:1e6f471e
2024-07-27 11:10:06
@ 0176967e:1e6f471e
2024-07-27 11:10:06Workshop je zameraný pre všetkých, ktorí sa potýkajú s vysvetľovaním Bitcoinu svojej rodine, kamarátom, partnerom alebo kolegom. Pri námietkach z druhej strany väčšinou ideme do protiútoku a snažíme sa vytiahnuť tie najlepšie argumenty. Na tomto workshope vás naučím nový prístup k zvládaniu námietok a vyskúšate si ho aj v praxi. Know-how je aplikovateľné nie len na komunikáciu Bitcoinu ale aj pre zlepšenie vzťahov, pri výchove detí a celkovo pre lepší osobný život.
-
 @ 0176967e:1e6f471e
2024-07-26 17:45:08
@ 0176967e:1e6f471e
2024-07-26 17:45:08Ak ste v Bitcoine už nejaký ten rok, možno máte pocit, že už všetkému rozumiete a že vás nič neprekvapí. Viete čo je to peňaženka, čo je to seed a čo adresa, možno dokonca aj čo je to sha256. Ste si istí? Táto prednáška sa vám to pokúsi vyvrátiť. 🙂
-
 @ 0176967e:1e6f471e
2024-07-26 12:15:35
@ 0176967e:1e6f471e
2024-07-26 12:15:35Bojovať s rakovinou metabolickou metódou znamená použiť metabolizmus tela proti rakovine. Riadenie cukru a ketónov v krvi stravou a pohybom, časovanie rôznych typov cvičení, včasná kombinácia klasickej onko-liečby a hladovania. Ktoré vitamíny a suplementy prijímam a ktorým sa napríklad vyhýbam dajúc na rady mojej dietologičky z USA Miriam (ktorá sa špecializuje na rakovinu).
Hovori sa, že čo nemeriame, neriadime ... Ja som meral, veľa a dlho ... aj grafy budú ... aj sranda bude, hádam ... 😉
-
 @ eb0157af:77ab6c55
2025-05-22 08:01:33
@ eb0157af:77ab6c55
2025-05-22 08:01:33Legal developments show that prosecutors may have concealed evidence in the case against the Tornado Cash mixer.
The legal case involving the Tornado Cash mixer may be at a turning point. Roman Storm’s legal team, one of the platform’s developers, has asked the court to reconsider the motion to dismiss the case, arguing that the prosecution deliberately withheld evidence favorable to the defense. These documents, originating from the Financial Crimes Enforcement Network (FinCEN) and dating back to 2023, would demonstrate that non-custodial cryptocurrency mixers like Tornado Cash do not fall under the legal definition of a “money transmitting business.”
According to a letter dated May 16 addressed to Judge Katherine Polk Failla, prosecutors were aware of FinCEN’s guidelines on cryptocurrency mixers but nonetheless proceeded with charges against the developers of both Samourai Wallet and Tornado Cash. The prosecution denies having withheld evidence, claiming it provided the FinCEN communications within the established deadlines during the discovery phase.

Source: Court Listener
Similarities with the Samourai Wallet case
Storm’s defense team cited the same legal documents and arguments presented by the attorneys for the Samourai Wallet developers in a legal letter dated May 5. The attorneys wrote:
“The disclosures in the Samourai case reveal that the government, at the very least, played fast and loose and, at worst, affirmatively misled this Court with its arguments about FinCEN guidance when responding to the motions to dismiss and to compel discovery.”
Although on April 28, federal judge Robert Pitman issued a ruling denying the Office of Foreign Assets Control (OFAC) the ability to reimpose sanctions on Tornado Cash — setting a legal precedent for cases involving non-custodial mixers — federal prosecutors are nonetheless moving forward with the case against Storm, albeit with modified charges.
The post Tornado Cash case: new evidence reveals potential procedural misconduct appeared first on Atlas21.
-
 @ 0176967e:1e6f471e
2024-07-26 09:50:53
@ 0176967e:1e6f471e
2024-07-26 09:50:53Predikčné trhy predstavujú praktický spôsob, ako môžeme nahliadnuť do budúcnosti bez nutnosti spoliehať sa na tradičné, často nepresné metódy, ako je veštenie z kávových zrniek. V prezentácii sa ponoríme do histórie a vývoja predikčných trhov, a popíšeme aký vplyv mali a majú na dostupnosť a kvalitu informácií pre širokú verejnosť, a ako menia trh s týmito informáciami. Pozrieme sa aj na to, ako tieto trhy umožňujú obyčajným ľuďom prístup k spoľahlivým predpovediam a ako môžu prispieť k lepšiemu rozhodovaniu v rôznych oblastiach života.
-
 @ 0176967e:1e6f471e
2024-07-25 20:53:07
@ 0176967e:1e6f471e
2024-07-25 20:53:07AI hype vnímame asi všetci okolo nás — už takmer každá appka ponúka nejakú “AI fíčuru”, AI startupy raisujú stovky miliónov a Európa ako obvykle pracuje na regulovaní a našej ochrane pred nebezpečím umelej inteligencie. Pomaly sa ale ukazuje “ovocie” spojenia umelej inteligencie a človeka, kedy mnohí ľudia reportujú signifikantné zvýšenie produktivity v práci ako aj kreatívnych aktivitách (aj napriek tomu, že mnohí hardcore kreatívci by každého pri spomenutí skratky “AI” najradšej upálili). V prvej polovici prednášky sa pozrieme na to, akými rôznymi spôsobmi nám vie byť AI nápomocná, či už v práci alebo osobnom živote.
Umelé neuróny nám už vyskakujú pomaly aj z ovsených vločiek, no to ako sa k nám dostávajú sa veľmi líši. Hlavne v tom, či ich poskytujú firmy v zatvorených alebo open-source modeloch. V druhej polovici prednášky sa pozrieme na boom okolo otvorených AI modelov a ako ich vieme využiť.
-
 @ eb0157af:77ab6c55
2025-05-22 07:01:12
@ eb0157af:77ab6c55
2025-05-22 07:01:12The exchange, which collapsed in 2022, will distribute $5 billion to creditors starting May 30.
On May 30, FTX will begin the second phase of repayments, delivering over $5 billion to eligible creditors. According to the official announcement, payments will be processed through two main providers: BitGo and Kraken.
Creditors can expect to receive their funds within a relatively short period — from one to three business days after the distribution begins. This second round focuses on creditors with claims over $50,000, following the first repayment phase launched in February for smaller claims.
John Ray III, current CEO of FTX, has allocated about $11.4 billion for customer repayments. Creditors will receive amounts calculated based on the value of crypto assets at the time of the bankruptcy filing (November 2022).
Variable repayment percentages
The distribution plan foresees differentiated payout rates based on the various categories of claims:
- Dotcom customer claims will receive 72%;
- U.S. customer claims will get 54%;
- General unsecured claims and claims from digital asset loans will each receive 61%;
- Convenience class claims will see a 120% repayment.
“These initial distributions to non-convenience classes mark a significant milestone for FTX,” stated the exchange’s CEO.
Requirements to claim repayments
To receive payments, creditors must complete several mandatory steps:
- Log into the FTX Customer Portal;
- Complete KYC (Know Your Customer) verification;
- Submit the required tax forms;
- Complete onboarding with BitGo or Kraken.
The post FTX: over $5 billion ready for creditors in second repayment phase appeared first on Atlas21.
-
 @ c9badfea:610f861a
2025-05-05 20:16:29
@ c9badfea:610f861a
2025-05-05 20:16:29- Install PocketPal (it's free and open source)
- Launch the app, open the menu, and navigate to Models
- Download one or more models (e.g. Phi, Llama, Qwen)
- Once downloaded, tap Load to start chatting
ℹ️ Experiment with different models and their quantizations (Q4, Q6, Q8, etc.) to find the most suitable one
-
 @ 088436cd:9d2646cc
2025-05-01 21:01:55
@ 088436cd:9d2646cc
2025-05-01 21:01:55The arrival of the coronavirus brought not only illness and death but also fear and panic. In such an environment of uncertainty, people have naturally stocked up on necessities, not knowing when things will return to normal.
Retail shelves have been cleared out, and even online suppliers like Amazon and Walmart are out of stock for some items. Independent sellers on these e-commerce platforms have had to fill the gap. With the huge increase in demand, they have found that their inventory has skyrocketed in value.
Many in need of these items (e.g. toilet paper, hand sanitizer and masks) balk at the new prices. They feel they are being taken advantage of in a time of need and call for intervention by the government to lower prices. The government has heeded that call, labeling the independent sellers as "price gougers" and threatening sanctions if they don't lower their prices. Amazon has suspended seller accounts and law enforcement at all levels have threatened to prosecute. Prices have dropped as a result and at first glance this seems like a victory for fair play. But, we will have to dig deeper to understand the unseen consequences of this intervention.
We must look at the economics of the situation, how supply and demand result in a price and how that price acts as a signal that goes out to everyone, informing them of underlying conditions in the economy and helping coordinate their actions.
It all started with a rise in demand. Given a fixed supply (e.g., the limited stock on shelves and in warehouses), an increase in demand inevitably leads to higher prices. Most people are familiar with this phenomenon, such as paying more for airline tickets during holidays or surge pricing for rides.
Higher prices discourage less critical uses of scarce resources. For example, you might not pay $1,000 for a plane ticket to visit your aunt if you can get one for $100 the following week, but someone else might pay that price to visit a dying relative. They value that plane seat more than you.
*** During the crisis, demand surged and their shelves emptied even though
However, retail outlets have not raised prices. They have kept them low, so the low-value uses of things like toilet paper, masks and hand sanitizer has continued. Often, this "use" just takes the form of hoarding. At everyday low prices, it makes sense to buy hundreds of rolls and bottles. You know you will use them eventually, so why not stock up? And, with all those extra supplies in the closet and basement, you don't need to change your behavior much. You don't have to ration your use.
At the low prices, these scarce resources got bought up faster and faster until there was simply none left. The reality of the situation became painfully clear to those who didn't panic and got to the store late: You have no toilet paper and you're not going to any time soon.
However, if prices had been allowed to rise, a number of effects would have taken place that would have coordinated the behavior of everyone so that valuable resources would not have been wasted or hoarded, and everyone could have had access to what they needed.
On the demand side, if prices had been allowed to rise, people would have begun to self-ration. You might leave those extra plies on the roll next time if you know they will cost ten times as much to replace. Or, you might choose to clean up a spill with a rag rather than disposable tissue. Most importantly, you won't hoard as much. That 50th bottle of hand sanitizer might just not be worth it at the new, high price. You'll leave it on the shelf for someone else who may have none.
On the supply side, higher prices would have incentivized people to offer up more of their stockpiles for sale. If you have a pallet full of toilet paper in your basement and all of the sudden they are worth $15 per roll, you might just list a few online. But, if it is illegal to do so, you probably won't.
Imagine you run a business installing insulation and have a few thousand respirator masks on hand for your employees. During a pandemic, it is much more important that people breathe filtered air than that insulation get installed, and that fact is reflected in higher prices. You will sell your extra masks at the higher price rather than store them for future insulation jobs, and the scarce resource will be put to its most important use.
Producers of hand sanitizer would go into overdrive if prices were allowed to rise. They would pay their employees overtime, hire new ones, and pay a premium for their supplies, making sure their raw materials don't go to less important uses.
These kinds of coordinated actions all across the economy would be impossible without real prices to guide them. How do you know if it makes sense to spend an extra $10k bringing a thousand masks to market unless you know you can get more than $10 per mask? If the price is kept artificially low, you simply can't do it. The money just isn't there.
These are the immediate effects of a price change, but incredibly, price changes also coordinate people's actions across space and time.
Across space, there are different supply and demand conditions in different places, and thus prices are not uniform. We know some places are real "hot spots" for the virus, while others are mostly unaffected. High demand in the hot spots leads to higher prices there, which attracts more of the resource to those areas. Boxes and boxes of essential items would pour in where they are needed most from where they are needed least, but only if prices were allowed to adjust freely.
This would be accomplished by individuals and businesses buying low in the unaffected areas, selling high in the hot spots and subtracting their labor and transportation costs from the difference. Producers of new supply would know exactly where it is most needed and ship to the high-demand, high-price areas first. The effect of these actions is to increase prices in the low demand areas and reduce them in the high demand areas. People in the low demand areas will start to self-ration more, reflecting the reality of their neighbors, and people in the hotspots will get some relief.
However, by artificially suppressing prices in the hot spot, people there will simply buy up the available supply and run out, and it will be cost prohibitive to bring in new supply from low-demand areas.
Prices coordinate economic actions across time as well. Just as entrepreneurs and businesses can profit by transporting scarce necessities from low-demand to high-demand areas, they can also profit by buying in low-demand times and storing their merchandise for when it is needed most.
Just as allowing prices to freely adjust in one area relative to another will send all the right signals for the optimal use of a scarce resource, allowing prices to freely adjust over time will do the same.
When an entrepreneur buys up resources during low-demand times in anticipation of a crisis, she restricts supply ahead of the crisis, which leads to a price increase. She effectively bids up the price. The change in price affects consumers and producers in all the ways mentioned above. Consumers self-ration more, and producers bring more of the resource to market.
Our entrepreneur has done a truly incredible thing. She has predicted the future, and by so doing has caused every individual in the economy to prepare for a shortage they don't even know is coming! And, by discouraging consumption and encouraging production ahead of time, she blunts the impact the crisis will have. There will be more of the resource to go around when it is needed most.
On top of this, our entrepreneur still has her stockpile she saved back when everyone else was blithely using it up. She can now further mitigate the damage of the crisis by selling her stock during the worst of it, when people are most desperate for relief. She will know when this is because the price will tell her, but only if it is allowed to adjust freely. When the price is at its highest is when people need the resource the most, and those willing to pay will not waste it or hoard it. They will put it to its highest valued use.
The economy is like a big bus we are all riding in, going down a road with many twists and turns. Just as it is difficult to see into the future, it is difficult to see out the bus windows at the road ahead.
On the dashboard, we don't have a speedometer or fuel gauge. Instead we have all the prices for everything in the economy. Prices are what tell us the condition of the bus and the road. They tell us everything. Without them, we are blind.
Good times are a smooth road. Consumer prices and interest rates are low, investment returns are steady. We hit the gas and go fast. But, the road is not always straight and smooth. Sometimes there are sharp turns and rough patches. Successful entrepreneurs are the ones who can see what is coming better than everyone else. They are our navigators.
When they buy up scarce resources ahead of a crisis, they are hitting the brakes and slowing us down. When they divert resources from one area to another, they are steering us onto a smoother path. By their actions in the market, they adjust the prices on our dashboard to reflect the conditions of the road ahead, so we can prepare for, navigate and get through the inevitable difficulties we will face.
Interfering with the dashboard by imposing price floors or price caps doesn't change the conditions of the road (the number of toilet paper rolls in existence hasn't changed). All it does is distort our perception of those conditions. We think the road is still smooth--our heavy foot stomping the gas--as we crash onto a rocky dirt road at 80 miles per hour (empty shelves at the store for weeks on end).
Supply, demand and prices are laws of nature. All of this is just how things work. It isn't right or wrong in a moral sense. Price caps lead to waste, shortages and hoarding as surely as water flows downhill. The opposite--allowing prices to adjust freely--leads to conservation of scarce resources and their being put to their highest valued use. And yes, it leads to profits for the entrepreneurs who were able to correctly predict future conditions, and losses for those who weren't.
Is it fair that they should collect these profits? On the one hand, anyone could have stocked up on toilet paper, hand sanitizer and face masks at any time before the crisis, so we all had a fair chance to get the supplies cheaply. On the other hand, it just feels wrong that some should profit so much at a time when there is so much need.
Our instinct in the moment is to see the entrepreneur as a villain, greedy "price gouger". But we don't see the long chain of economic consequences the led to the situation we feel is unfair.
If it weren't for anti-price-gouging laws, the major retailers would have raised their prices long before the crisis became acute. When they saw demand outstrip supply, they would have raised prices, not by 100 fold, but gradually and long before anyone knew how serious things would have become. Late comers would have had to pay more, but at least there would be something left on the shelf.
As an entrepreneur, why take risks trying to anticipate the future if you can't reap the reward when you are right? Instead of letting instead of letting entrepreneurs--our navigators--guide us, we are punishing and vilifying them, trying to force prices to reflect a reality that simply doesn't exist.
In a crisis, more than any other time, prices must be allowed to fluctuate. To do otherwise is to blind ourselves at a time when danger and uncertainty abound. It is economic suicide.
In a crisis, there is great need, and the way to meet that need is not by pretending it's not there, by forcing prices to reflect a world where there isn't need. They way to meet the need is the same it has always been, through charity.
If the people in government want to help, the best way for the to do so is to be charitable and reduce their taxes and fees as much as possible, ideally to zero in a time of crisis. Amazon, for example, could instantly reduce the price of all crisis related necessities by 20% if they waived their fee. This would allow for more uses by more people of these scarce supplies as hoarders release their stockpiles on to the market, knowing they can get 20% more for their stock. Governments could reduce or eliminate their tax burden on high-demand, crisis-related items and all the factors that go into their production, with the same effect: a reduction in prices and expansion of supply. All of us, including the successful entrepreneurs and the wealthy for whom high prices are not a great burden, could donate to relief efforts.
These ideas are not new or untested. This is core micro economics. It has been taught for hundreds of years in universities the world over. The fact that every crisis that comes along stirs up ire against entrepreneurs indicates not that the economics is wrong, but that we have a strong visceral reaction against what we perceive to be unfairness. This is as it should be. Unfairness is wrong and the anger it stirs in us should compel us to right the wrong. Our anger itself isn't wrong, it's just misplaced.
Entrepreneurs didn't cause the prices to rise. Our reaction to a virus did that. We saw a serious threat and an uncertain future and followed our natural impulse to hoard. Because prices at major retail suppliers didn't rise, that impulse ran rampant and we cleared the shelves until there was nothing left. We ran the bus right off the road and them blamed the entrepreneurs for showing us the reality of our situation, for shaking us out of the fantasy of low prices.
All of this is not to say that entrepreneurs are high-minded public servants. They are just doing their job. Staking your money on an uncertain future is a risky business. There are big risks and big rewards. Most entrepreneurs just scrape by or lose their capital in failed ventures.
However, the ones that get it right must be allowed to keep their profits, or else no one will try and we'll all be driving blind. We need our navigators. It doesn't even matter if they know all the positive effects they are having on the rest of us and the economy as a whole. So long as they are buying low and selling high--so long as they are doing their job--they will be guiding the rest of us through the good times and the bad, down the open road and through the rough spots.
-
 @ fbf0e434:e1be6a39
2025-05-22 06:52:22
@ fbf0e434:e1be6a39
2025-05-22 06:52:22Hackathon 概要
AI BUIDL Lab: 基于提示工程(Prompt Engineering)在 Rootstock 上构建真实 Web3 应用的黑客松 近日收官,共有 211 名开发者注册并提交 22 个项目。本次活动旨在鼓励开发者借助 AI 驱动的工作流程,在 Rootstock 平台开发 Web3 应用。参与者聚焦三大领域:去中心化金融(DeFi)与支付、商业与零工经济,以及 Web3 身份与声誉体系,通过 AI 技术加速去中心化应用(dApps)的创新迭代。
活动产出丰硕成果,包括去中心化金融解决方案、AI 增强型身份管理系统等,凸显了 AI 与 Web3 集成的潜力。赛事奖金池包含 1.5 万美元的 RIF 代币,用于奖励在创意性和技术执行力方面表现突出的顶尖项目。
本次黑客松不仅印证了 AI 在简化去中心化应用开发中的价值,也展现了 Web3 生态系统的进阶成果。活动与 thirdweb、Alchemy 及 RootstockLabs 的合作,为开发者高效参与及产出创新项目提供了有力支持。
Hackathon 获奖者
DeFi 和支付奖项得主
- ProtectedPay_Rootstock:一个在 CrossFi 链上的 DeFi 平台,通过先进的区块链功能促进安全转账、群体支付和智能储蓄。
- AIFi: AI-Powered DeFi Hub on Rootstock:利用 AI 提供汇款、信用评分和用户界面改善,提高拉丁美洲的金融可访问性。
商业和零工经济奖项得主
Web3 中的身份和声誉奖项得主
- AgenticID:提供自我主权身份验证,结合区块链和 AI,使用零知识证明进行安全的用户认证。
- TrustScan:使用 AI 分析 Rootstock 上的钱包活动,生成信誉和身份评分,加强信任。
赏金最佳 AI 提示使用
- AuditFi_Rootstock:提供 AI 驱动的智能合约安全审计,通过链上验证增强透明度和信任。
- RSK Smart Yield Engine:一个 AI 驱动的 DeFi 协议收益优化器,通过智能合约和 AI 管理资金和制定策略。
有关所有项目的更多信息,请访问 DoraHacks。
关于组织者
Rootstock
Rootstock - 比特币 DeFi 层 - 专注于将比特币强大的网络与以太坊的智能合约功能相结合,提升区块链的互操作性。Rootstock 以技术专长著称,已经创建了一个支持去中心化金融应用的平台。该组织致力于通过扩展在金融服务中智能合约的可访问性和功能性来推动区块链领域的创新。
-
 @ 6ad3e2a3:c90b7740
2025-05-20 13:49:50
@ 6ad3e2a3:c90b7740
2025-05-20 13:49:50I’ve written about MSTR twice already, https://www.chrisliss.com/p/mstr and https://www.chrisliss.com/p/mstr-part-2, but I want to focus on legendary short seller James Chanos’ current trade wherein he buys bitcoin (via ETF) and shorts MSTR, in essence to “be like Mike” Saylor who sells MSTR shares at the market and uses them to add bitcoin to the company’s balance sheet. After all, if it’s good enough for Saylor, why shouldn’t everyone be doing it — shorting a company whose stock price is more than 2x its bitcoin holdings and using the proceeds to buy the bitcoin itself?
Saylor himself has said selling shares at 2x NAV (net asset value) to buy bitcoin is like selling dollars for two dollars each, and Chanos has apparently decided to get in while the getting (market cap more than 2x net asset value) is good. If the price of bitcoin moons, sending MSTR’s shares up, you are more than hedged in that event, too. At least that’s the theory.
The problem with this bet against MSTR’s mNAV, i.e., you are betting MSTR’s market cap will converge 1:1 toward its NAV in the short and medium term is this trade does not exist in a vacuum. Saylor has described how his ATM’s (at the market) sales of shares are accretive in BTC per share because of this very premium they carry. Yes, we’ll dilute your shares of the company, but because we’re getting you 2x the bitcoin per share, you are getting an ever smaller slice of an ever bigger overall pie, and the pie is growing 2x faster than your slice is reducing. (I https://www.chrisliss.com/p/mstr how this works in my first post.)
But for this accretion to continue, there must be a constant supply of “greater fools” to pony up for the infinitely printable shares which contain only half their value in underlying bitcoin. Yes, those shares will continue to accrete more BTC per share, but only if there are more fools willing to make this trade in the future. So will there be a constant supply of such “fools” to keep fueling MSTR’s mNAV multiple indefinitely?
Yes, there will be in my opinion because you have to look at the trade from the prospective fools’ perspective. Those “fools” are not trading bitcoin for MSTR, they are trading their dollars, selling other equities to raise them maybe, but in the end it’s a dollars for shares trade. They are not selling bitcoin for them.
You might object that those same dollars could buy bitcoin instead, so they are surely trading the opportunity cost of buying bitcoin for them, but if only 5-10 percent of the market (or less) is buying bitcoin itself, the bucket in which which those “fools” reside is the entire non-bitcoin-buying equity market. (And this is not considering the even larger debt market which Saylor has yet to tap in earnest.)
So for those 90-95 percent who do not and are not presently planning to own bitcoin itself, is buying MSTR a fool’s errand, so to speak? Not remotely. If MSTR shares are infinitely printable ATM, they are still less so than the dollar and other fiat currencies. And MSTR shares are backed 2:1 by bitcoin itself, while the fiat currencies are backed by absolutely nothing. So if you hold dollars or euros, trading them for MSTR shares is an errand more sage than foolish.
That’s why this trade (buying BTC and shorting MSTR) is so dangerous. Not only are there many people who won’t buy BTC buying MSTR, there are many funds and other investment entities who are only able to buy MSTR.
Do you want to get BTC at 1:1 with the 5-10 percent or MSTR backed 2:1 with the 90-95 percent. This is a bit like medical tests that have a 95 percent accuracy rate for an asymptomatic disease that only one percent of the population has. If someone tests positive, it’s more likely to be a false one than an indication he has the disease*. The accuracy rate, even at 19:1, is subservient to the size of the respective populations.
At some point this will no longer be the case, but so long as the understanding of bitcoin is not widespread, so long as the dollar is still the unit of account, the “greater fools” buying MSTR are still miles ahead of the greatest fools buying neither, and the stock price and mNAV should only increase.
. . .
One other thought: it’s more work to play defense than offense because the person on offense knows where he’s going, and the defender can only react to him once he moves. Similarly, Saylor by virtue of being the issuer of the shares knows when more will come online while Chanos and other short sellers are borrowing them to sell in reaction to Saylor’s strategy. At any given moment, Saylor can pause anytime, choosing to issue convertible debt or preferred shares with which to buy more bitcoin, and the shorts will not be given advance notice.
If the price runs, and there is no ATM that week because Saylor has stopped on a dime, so to speak, the shorts will be left having to scramble to change directions and buy the shares back to cover. Their momentum might be in the wrong direction, though, and like Allen Iverson breaking ankles with a crossover, Saylor might trigger a massive short squeeze, rocketing the share price ever higher. That’s why he actually welcomes Chanos et al trying this copycat strategy — it becomes the fuel for outsized gains.
For that reason, news that Chanos is shorting MSTR has not shaken my conviction, though there are other more pertinent https://www.chrisliss.com/p/mstr-part-2 with MSTR, of which one should be aware. And as always, do your own due diligence before investing in anything.
* To understand this, consider a population of 100,000, with one percent having a disease. That means 1,000 have it, 99,000 do not. If the test is 95 percent accurate, and everyone is tested, 950 of the 1,000 will test positive (true positives), 50 who have it will test negative (false negatives.) Of the positives, 95 percent of 99,000 (94,050) will test negative (true negatives) and five percent (4,950) will test positive (false positives). That means 4,950 out of 5,900 positives (84%) will be false.
-
 @ c1e9ab3a:9cb56b43
2025-05-18 04:14:48
@ c1e9ab3a:9cb56b43
2025-05-18 04:14:48Abstract
This document proposes a novel architecture that decouples the peer-to-peer (P2P) communication layer from the Bitcoin protocol and replaces or augments it with the Nostr protocol. The goal is to improve censorship resistance, performance, modularity, and maintainability by migrating transaction propagation and block distribution to the Nostr relay network.
Introduction
Bitcoin’s current architecture relies heavily on its P2P network to propagate transactions and blocks. While robust, it has limitations in terms of flexibility, scalability, and censorship resistance in certain environments. Nostr, a decentralized event-publishing protocol, offers a multi-star topology and a censorship-resistant infrastructure for message relay.
This proposal outlines how Bitcoin communication could be ported to Nostr while maintaining consensus and verification through standard Bitcoin clients.
Motivation
- Enhanced Censorship Resistance: Nostr’s architecture enables better relay redundancy and obfuscation of transaction origin.
- Simplified Lightweight Nodes: Removing the full P2P stack allows for lightweight nodes that only verify blockchain data and communicate over Nostr.
- Architectural Modularity: Clean separation between validation and communication enables easier auditing, upgrades, and parallel innovation.
- Faster Propagation: Nostr’s multi-star network may provide faster propagation of transactions and blocks compared to the mesh-like Bitcoin P2P network.
Architecture Overview
Components
-
Bitcoin Minimal Node (BMN):
- Verifies blockchain and block validity.
- Maintains UTXO set and handles mempool logic.
- Connects to Nostr relays instead of P2P Bitcoin peers.
-
Bridge Node:
- Bridges Bitcoin P2P traffic to and from Nostr relays.
- Posts new transactions and blocks to Nostr.
- Downloads mempool content and block headers from Nostr.
-
Nostr Relays:
- Accept Bitcoin-specific event kinds (transactions and blocks).
- Store mempool entries and block messages.
- Optionally broadcast fee estimation summaries and tipsets.
Event Format
Proposed reserved Nostr
kindnumbers for Bitcoin content (NIP/BIP TBD):| Nostr Kind | Purpose | |------------|------------------------| | 210000 | Bitcoin Transaction | | 210001 | Bitcoin Block Header | | 210002 | Bitcoin Block | | 210003 | Mempool Fee Estimates | | 210004 | Filter/UTXO summary |
Transaction Lifecycle
- Wallet creates a Bitcoin transaction.
- Wallet sends it to a set of configured Nostr relays.
- Relays accept and cache the transaction (based on fee policies).
- Mining nodes or bridge nodes fetch mempool contents from Nostr.
- Once mined, a block is submitted over Nostr.
- Nodes confirm inclusion and update their UTXO set.
Security Considerations
- Sybil Resistance: Consensus remains based on proof-of-work. The communication path (Nostr) is not involved in consensus.
- Relay Discoverability: Optionally bootstrap via DNS, Bitcoin P2P, or signed relay lists.
- Spam Protection: Relay-side policy, rate limiting, proof-of-work challenges, or Lightning payments.
- Block Authenticity: Nodes must verify all received blocks and reject invalid chains.
Compatibility and Migration
- Fully compatible with current Bitcoin consensus rules.
- Bridge nodes preserve interoperability with legacy full nodes.
- Nodes can run in hybrid mode, fetching from both P2P and Nostr.
Future Work
- Integration with watch-only wallets and SPV clients using verified headers via Nostr.
- Use of Nostr’s social graph for partial trust assumptions and relay reputation.
- Dynamic relay discovery using Nostr itself (relay list events).
Conclusion
This proposal lays out a new architecture for Bitcoin communication using Nostr to replace or augment the P2P network. This improves decentralization, censorship resistance, modularity, and speed, while preserving consensus integrity. It encourages innovation by enabling smaller, purpose-built Bitcoin nodes and offloading networking complexity.
This document may become both a Bitcoin Improvement Proposal (BIP-XXX) and a Nostr Improvement Proposal (NIP-XXX). Event kind range reserved: 210000–219999.
-
 @ 90152b7f:04e57401
2025-05-22 03:51:20
@ 90152b7f:04e57401
2025-05-22 03:51:20Wikileaks - S E C R E T SECTION 01 OF 02 TEL AVIV 001733 SIPDIS SIPDIS E.O. 12958: DECL: 06/13/2017 TAGS: PREL, PTER, MOPS, KWBG, LE, SY, IS SUBJECT: MILITARY INTELLIGENCE DIRECTOR YADLIN COMMENTS ON GAZA, SYRIA AND LEBANON Classified By: Ambassador Richard H. Jones, Reason 1.4 (b) (d)
2007 June 13
1. (S) Summary. During a June 12 meeting with the Ambassador, IDI Director MG Amos Yadlin said that Gaza was "number four" on his list of threats, preceded by Iran, Syria, and Hizballah in that order. Yadlin said the IDI has been predicting armed confrontation in Gaza between Hamas and Fatah since Hamas won the January 2006 legislative council elections. Yadlin felt that the Hamas military wing had initiated the current escalation with the tacit consent of external Hamas leader Khalid Mishal, adding that he did not believe there had been a premeditated political-level decision by Hamas to wipe out Fatah in Gaza. Yadlin dismissed Fatah's capabilities in Gaza, saying Hamas could have taken over there any time it wanted for the past year, but he agreed that Fatah remained strong in the West Bank. Although not necessarily reflecting a GOI consensus view, Yadlin said Israel would be "happy" if Hamas took over Gaza because the IDF could then deal with Gaza as a hostile state. He dismissed the significance of an Iranian role in a Hamas-controlled Gaza "as long as they don't have a port." Regarding predictions of war with Syria this summer, Yadlin recalled the lead-up to the 1967 war, which he said was provoked by the Soviet Ambassador in Israel. Both Israel and Syria are in a state of high alert, so war could happen easily even though neither side is seeking it. Yadlin suggested that the Asad regime would probably not survive a war, but added that Israel was no longer concerned with maintaining that "evil" regime. On Lebanon, Yadlin felt that the fighting in the Nahr Al-Barid camp was a positive development for Israel since it had "embarrassed" Hizballah, adding that IDI had information that the Fatah Al-Islam terrorist group was planning to attack UNIFIL before it blundered into its confrontation with the LAF. End Summary.
Gaza Fighting Not Israel's Main Problem
---------------------------------------
2. (S) The Ambassador, accompanied by Pol Couns and DATT, called on IDI Director Major General Amos Yadlin June 12. Noting reports of fierce fighting between Hamas and Fatah in Gaza that day, the Ambassador asked for Yadlin's assessment. Yadlin described Gaza as "not Israel's main problem," noting that it ranked fourth in his hierarchy of threats, behind Iran, Syria, and Hizballah. Yadlin described Gaza as "hopeless for now," commenting that the Palestinians had to realize that Hamas offered no solution. IDI analysts, he said, had predicted a confrontation in Gaza since Hamas won the Palestinian Legislative Council elections in January 2006. Yadlin commented that Palestinian President Mahmoud Abbas and Hamas Prime Minister Ismail Haniyeh had become personally close despite their ideological differences, but neither leader had control over those forces under them.
3. (S) Yadlin explained that both Fatah and Hamas contained many factions. The Hamas military wing had been frustrated since the signing of the Mecca Agreement in January, but there were also many armed groups in Gaza that were not under the control of either party. Yadlin cited the example of the Dughmush clan, which had shifted from Fatah to the Popular Resistance Committees to Hamas before becoming an armed entity opposed to all of them. After May 15, the Hamas military wing had sought to export the fighting to Sderot by launching waves of Qassam rockets. One week later, as a result of IDF retaliation, they realized the price was too high and reduced the Qassam attacks.
4. (S) In response to the Ambassador's question, Yadlin said he did not think that day's Hamas attacks on Fatah security forces were part of a premeditated effort to wipe out Fatah in Gaza. Instead, they probably represented an initiative of the military wing with the tacit consent of Khalid Mishal in Damascus. Mishal was still considering the costs and benefits of the fighting, but the situation had become so tense that any incident could lead to street fighting without any political decision.
Gaza and West Bank Separating
-----------------------------
5. (S) The Ambassador asked Yadlin for his assessment of reports that Fatah forces had been ordered not to fight back. Yadlin said Mohammed Dahlan had 500 men and the Presidential Guard had 1,500 more. They understand that the balance of power favors Hamas, which "can take over Gaza any time it wants to." Yadlin said he would be surprised if Fatah fights, and even more surprised if they win. As far as he was concerned, this had been the case for the past year. The situation was different in the West Bank, however, where Fatah remained relatively strong and had even started to
TEL AVIV 00001733 002 OF 002
kidnap Hamas activists. Yadlin agreed that Tawfiq Tirawi had a power base in the West Bank, but he added that Fatah was not cohesive.
6. (S) The Ambassador commented that if Fatah decided it has lost Gaza, there would be calls for Abbas to set up a separate regime in the West Bank. While not necessarily reflecting a consensus GOI view, Yadlin commented that such a development would please Israel since it would enable the IDF to treat Gaza as a hostile country rather than having to deal with Hamas as a non-state actor. He added that Israel could work with a Fatah regime in the West Bank. The Ambassador asked Yadlin if he worried about a Hamas-controlled Gaza giving Iran a new opening. Yadlin replied that Iran was already present in Gaza, but Israel could handle the situation "as long as Gaza does not have a port (sea or air)."
War with Syria "Could Happen Easily"
------------------------------------
7. (S) Noting Israeli press speculation, the Ambassador asked Yadlin if he expected war with Syria this summer. Recalling the 1967 war, Yadlin commented that it had started as a result of the Soviet Ambassador in Israel reporting on non-existing Israeli preparations to attack Syria. Something similar was happening again, he said, with the Russians telling the Syrians that Israel planned to attack them, possibly in concert with a U.S. attack on Iran. Yadlin stated that since last summer's war in Lebanon, Syria had engaged in a "frenzy of preparations" for a confrontation with Israel. The Syrian regime was also showing greater self-confidence. Some Syrian leaders appeared to believe that Syria could take on Israel military, but others were more cautious. The fact that both sides were on high alert meant that a war could happen easily, even though neither side is seeking one. In response to a question, Yadlin said he did not think the Asad regime would survive a war, but he added that preserving that "evil" regime should not be a matter of concern.
Fighting in Nahr al-Barid Positive for Israel
---------------------------------------------
8. (S) The Ambassador asked Yadlin for his views on the fighting in the Nahr al-Barid refugee camp in northern Lebanon. Although Yadlin was called to another meeting and did not have time to elaborate, he answered that the fighting was positive for Israel because it had embarrassed Hizballah, which had been unable to adopt a clear-cut position on the Lebanese Army's action, and because the Fatah al-Islam terrorist organization had been planning to attack UNIFIL and then Israel before it blundered into its current confrontation with the LAF. He also agreed that the confrontation was strengthening the LAF, in fact and in the eyes of the Lebanese people, which was also good.
9. (S) Comment: Yadlin's relatively relaxed attitude toward the deteriorating security situation in Gaza represents a shift in IDF thinking from last fall, when the Southern Command supported a major ground operation into Gaza to remove the growing threat from Hamas. While many media commentators continue to make that argument, Yadlin's view appears to be more in synch with that of Chief of General Staff Ashkenazi, who also believes that the more serious threat to Israel currently comes from the north.
********************************************* ******************** Visit Embassy Tel Aviv's Classified Website: http://www.state.sgov.gov/p/nea/telaviv
You can also access this site through the State Department's Classified SIPRNET website. ********************************************* ******************** JONES
-
 @ 866e0139:6a9334e5
2025-05-22 06:51:15
@ 866e0139:6a9334e5
2025-05-22 06:51:15Autor: Milosz Matuschek. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie auch in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
https://www.youtube.com/watch?v=gjndTXyk3mw
Im Jahr 1954, als Frankreich gerade dabei war, seine kolonialen Kriege in Indochina und Algerien zu verschärfen, schrieb Boris Vian ein Lied – oder vielmehr: einen poetischen Faustschlag. Le Déserteur ist keine Ballade, sondern ein Manifest. Keine Hymne auf den Frieden, sondern eine Anklage gegen den Krieg. Adressiert an den Präsidenten, beginnt das Chanson wie ein höflicher Brief – und endet als flammender Akt des zivilen Ungehorsams.
„Herr Präsident,\ ich schreibe Ihnen einen Brief,\ den Sie vielleicht lesen werden,\ wenn Sie Zeit haben.“
Was folgt, ist ein klassischer Kriegsdienstverweigerungsbrief, aber eben kein bürokratischer. Vian spricht nicht in Paragraphen, sondern in Herzschlägen. Der Erzähler, ein einfacher Mann, will nicht kämpfen. Nicht für irgendein Vaterland, nicht für irgendeine Fahne, nicht für irgendeinen ideologischen Zweck.
„Ich soll zur Welt gekommen sein,\ um zu leben, nicht um zu sterben.“
70 Jahre später klingt diese Zeile wie ein Skandal. In einer Zeit, in der die Ukraine junge Männer für Kopfgeld auf der Straße zwangsrekrutiert und in Stahlgewitter schickt, in der palästinensische Jugendliche im Gazastreifen unter Trümmern begraben werden, während israelische Reservisten mit Dauerbefehl marschieren – ist Le Déserteur ein sakraler Text geworden. Fast ein Gebet.
„Wenn man mich verfolgt,\ werde ich den Gehorsam verweigern.\ Ich werde keine Waffe in die Hand nehmen,\ ich werde fliehen, bis ich Frieden finde.“
Wie viele „Deserteure“ gibt es heute, die wir gar nicht kennen? Menschen, die sich nicht auf die Seite der Bomben stellen wollen – egal, wer sie wirft? Die sich nicht mehr einspannen lassen zwischen Propaganda und Patriotismus? Die ihre Menschlichkeit über jeden nationalen Befehl stellen?
Der Krieg, sagt Vian, macht aus freien Menschen Befehlsempfänger und aus Söhnen Leichen. Und wer heute sagt, es gebe „gerechte Kriege“, sollte eine Frage beantworten: Ist es auch ein gerechter Tod?
Darum: Verweigert.
Verweigert den Befehl, zu hassen.\ Verweigert den Reflex, Partei zu ergreifen.\ Verweigert den Dienst an der Waffe.
Denn wie Vian singt:
„Sagen Sie's den Leuten:\ Ich werde nicht kommen.“
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 0176967e:1e6f471e
2024-07-25 20:38:11
@ 0176967e:1e6f471e
2024-07-25 20:38:11Čo vznikne keď spojíš hru SNAKE zo starej Nokie 3310 a Bitcoin? - hra Chain Duel!
Jedna z najlepších implementácií funkcionality Lightning Networku a gamingu vo svete Bitcoinu.
Vyskúšať si ju môžete s kamošmi na tomto odkaze. Na stránke nájdeš aj základné pravidlá hry avšak odporúčame pravidlá pochopiť aj priamo hraním
Chain Duel si získava hromady fanúšikov po bitcoinových konferenciách po celom svete a práve na Lunarpunk festival ho prinesieme tiež.
Multiplayer 1v1 hra, kde nejde o náhodu, ale skill, vás dostane. Poďte si zmerať sily s ďalšími bitcoinermi a vyhrať okrem samotných satoshi rôzne iné ceny.
Príďte sa zúčastniť prvého oficiálneho Chain Duel turnaja na Slovensku!
Pre účasť na turnaji je potrebná registrácia dopredu.
-
 @ 0176967e:1e6f471e
2024-07-22 19:57:47
@ 0176967e:1e6f471e
2024-07-22 19:57:47Co se nomádská rodina již 3 roky utíkající před kontrolou naučila o kontrole samotné? Co je to vlastně svoboda? Může koexistovat se strachem? S konfliktem? Zkusme na chvíli zapomenout na daně, policii a stát a pohlédnout na svobodu i mimo hranice společenských ideologií. Zkusme namísto hledání dalších odpovědí zjistit, zda se ještě někde neukrývají nové otázky. Možná to bude trochu ezo.
Karel provozuje již přes 3 roky se svou ženou, dvěmi dětmi a jedním psem minimalistický život v obytné dodávce. Na cestách spolu začali tvořit youtubový kanál "Karel od Martiny" o svobodě, nomádství, anarchii, rodičovství, drogách a dalších normálních věcech.
Nájdete ho aj na nostr.
-
 @ 418a17eb:b64b2b3a
2025-04-26 21:45:33
@ 418a17eb:b64b2b3a
2025-04-26 21:45:33In today’s world, many people chase after money. We often think that wealth equals success and happiness. But if we look closer, we see that money is just a tool. The real goal is freedom.
Money helps us access resources and experiences. It can open doors. But the constant pursuit of wealth can trap us. We may find ourselves stressed, competing with others, and feeling unfulfilled. The more we chase money, the more we might lose sight of what truly matters.
Freedom, on the other hand, is about choice. It’s the ability to live life on our own terms. When we prioritize freedom, we can follow our passions and build meaningful relationships. We can spend our time on what we love, rather than being tied down by financial worries.
True fulfillment comes from this freedom. It allows us to define success for ourselves. When we embrace freedom, we become more resilient and creative. We connect more deeply with ourselves and others. This sense of purpose often brings more happiness than money ever could.
In the end, money isn’t the ultimate goal. It’s freedom that truly matters. By focusing on living authentically and making choices that resonate with us, we can create a life filled with meaning and joy.
-
 @ 0176967e:1e6f471e
2024-07-21 15:48:56
@ 0176967e:1e6f471e
2024-07-21 15:48:56Lístky na festival Lunarpunku sú už v predaji na našom crowdfunding portáli. V predaji sú dva typy lístkov - štandardný vstup a špeciálny vstup spolu s workshopom oranžového leta.
Neváhajte a zabezpečte si lístok, čím skôr to urobíte, tým bude festival lepší.
Platiť môžete Bitcoinom - Lightningom aj on-chain. Vaša vstupenka je e-mail adresa (neposielame potvrdzujúce e-maily, ak platba prešla, ste in).
-
 @ 7460b7fd:4fc4e74b
2025-05-17 08:26:13
@ 7460b7fd:4fc4e74b
2025-05-17 08:26:13背景:WhatsApp的号码验证与运营商合作关系
作为一款基于手机号码注册的即时通信应用,WhatsApp的账号验证严重依赖全球电信运营商提供的短信或电话服务。这意味着,当用户注册或在新设备登录WhatsApp时,WhatsApp通常会向用户的手机号码发送SMS短信验证码或发起语音电话验证。这一流程利用了传统电信网络的基础设施,例如通过SS7(信令系统7)协议在全球范围内路由短信和电话securityaffairs.com。换句话说,WhatsApp把初始账户验证的安全性建立在电信运营商网络之上。然而,这种依赖关系也带来了隐患:攻击者可以利用电信网络的漏洞来拦截验证码。例如,研究人员早在2016年就演示过利用SS7协议漏洞拦截WhatsApp和Telegram的验证短信,从而劫持用户账户的攻击方法securityaffairs.com。由于SS7协议在全球范围内连接各国运营商,一个运营商的安全缺陷或恶意行为都可能被不法分子利用来获取他网用户的短信验证码securityaffairs.com。正因如此,有安全专家指出,仅依赖短信验证不足以保障账户安全,WhatsApp等服务提供商需要考虑引入额外机制来核实用户身份securityaffairs.com。
除了技术漏洞,基于电信运营商的验证还受到各地政策和网络环境影响。WhatsApp必须与全球各地运营商“合作”,才能将验证码送达到用户手机。然而这种“合作”在某些国家可能并不顺畅,典型例子就是中国。在中国大陆,国际短信和跨境电话常受到严格管控,WhatsApp在发送验证码时可能遭遇拦截或延迟sohu.com。因此,理解WhatsApp在中国的特殊联网和验证要求,需要将其全球验证机制与中国的电信政策和网络审查环境联系起来。下文将深入探讨为什么在中国使用WhatsApp进行号码验证时,必须开启蜂窝移动数据,并分析其中的技术逻辑和政策因素。
中国环境下的特殊问题:为何必须开启蜂窝数据?
中国的网络审查与封锁: WhatsApp自2017年起就在中国大陆遭遇严格封锁。起初,WhatsApp在华的服务受到**“GFW”(防火长城)**的部分干扰——例如曾一度只能发送文本消息,语音、视频和图片消息被封锁theguardian.com。到2017年下半年,封锁升级,很多用户报告在中国完全无法使用WhatsApp收发任何消息theguardian.com。中国官方将WhatsApp与Facebook、Telegram等西方通信平台一同屏蔽,视作对国家网络主权的挑战theguardian.com。鉴于此,在中国境内直接访问WhatsApp的服务器(无论通过Wi-Fi还是本地互联网)都会被防火长城所阻断。即使用户收到了短信验证码,WhatsApp客户端也无法在没有特殊连接手段的情况下与服务器完成验证通信。因此,单纯依赖Wi-Fi等本地网络环境往往无法完成WhatsApp的注册或登陆。很多用户经验表明,在中国使用WhatsApp时需要借助VPN等工具绕过审查,同时尽可能避免走被审查的网络路径sohu.com。
强制Wi-Fi热点与连接策略: 除了国家级的封锁,用户所连接的局域网络也可能影响WhatsApp验证。许多公共Wi-Fi(如机场、商场)采取强制门户认证(captive portal),用户需登录认证后才能上网。对此,WhatsApp在客户端内置了检测机制,当发现设备连入这类强制Wi-Fi热点而无法访问互联网时,会提示用户忽略该Wi-Fi并改用移动数据faq.whatsapp.com。WhatsApp要求对此授予读取Wi-Fi状态的权限,以便在检测到被拦截时自动切换网络faq.whatsapp.com。对于中国用户来说,即便所连Wi-Fi本身联网正常,由于GFW的存在WhatsApp依然可能视之为“不通畅”的网络环境。这也是WhatsApp官方指南中强调:如果Wi-Fi网络无法连接WhatsApp服务,应直接切换到手机的移动数据网络faq.whatsapp.com。在中国,由于本地宽带网络对WhatsApp的封锁,蜂窝数据反而成为相对可靠的通道——尤其在搭配VPN时,可以避开本地ISP的审查策略,实现与WhatsApp服务器的通信sohu.com。
国际短信的运营商限制: 使用移动数据还有助于解决短信验证码接收难题。中国的手机运营商出于防垃圾短信和安全考虑,默认对国际短信和境外来电进行一定限制。许多中国用户发现,注册WhatsApp时迟迟收不到验证码短信,原因可能在于运营商将来自国外服务号码的短信拦截或过滤sohu.com。例如,中国移动默认关闭国际短信接收,需要用户主动发送短信指令申请开通sohu.com。具体而言,中国移动用户需发送文本“11111”到10086(或10085)来开通国际短信收发权限;中国联通和电信用户也被建议联系运营商确认未屏蔽国际短信sohu.com。若未进行这些设置,WhatsApp发送的验证码短信可能根本无法抵达用户手机。在这种情况下,WhatsApp提供的备用方案是语音电话验证,即通过国际电话拨打用户号码并播报验证码。然而境外来电在中国也可能遭到运营商的安全拦截,特别是当号码被认为可疑时zhuanlan.zhihu.com。因此,中国用户经常被建议开启手机的蜂窝数据和漫游功能,以提高验证码接收的成功率sohu.com。一方面,开启数据漫游意味着用户准备接受来自境外的通信(通常也包含短信/电话);另一方面,在数据联网的状态下,WhatsApp可以尝试通过网络直接完成验证通信,从而减少对SMS的依赖。
移动数据的网络路径优势: 在实际案例中,一些中国WhatsApp用户报告仅在开启蜂窝数据的情况下才能完成验证。这可能归因于蜂窝网络和宽带网络在国际出口上的差异。中国移动、联通等运营商的移动数据可能走与宽带不同的网关路由,有时对跨境小流量的拦截相对宽松。此外,WhatsApp在移动数据环境中可以利用一些底层网络特性。例如,WhatsApp可能通过移动网络发起某些专用请求或利用运营商提供的号码归属地信息进行辅助验证(虽然具体实现未公开,但这是业界讨论的可能性)。总之,在中国特殊的网络环境下,开启蜂窝数据是确保WhatsApp验证流程顺利的重要一步。这一步不仅是为了基本的互联网连接,也是为了绕开种种对国际短信和应用数据的拦截限制,从而与WhatsApp的全球基础设施建立必要的通讯。
PDP Context与IMSI:移动网络验证的技术细节
要理解为什么移动数据对WhatsApp验证如此关键,有必要了解移动通信网络中的一些技术细节,包括PDP Context和IMSI的概念。
PDP Context(分组数据协议上下文): 当手机通过蜂窝网络使用数据(如4G/5G上网)时,必须先在运营商核心网中建立一个PDP上下文。这实际上就是申请开启一个数据会话,运营商将为设备分配一个IP地址,并允许其通过移动核心网访问互联网datascientest.com。PDP上下文包含了一系列参数(例如APN接入点名称、QoS等级等),描述该数据会话的属性datascientest.comdatascientest.com。简单来说,激活蜂窝数据就意味着创建了PDP上下文,设备获得了移动网络网关分配的IP地址,可以收发数据包。对于WhatsApp验证而言,只有在建立数据连接后,手机才能直接与WhatsApp的服务器交换数据,例如提交验证码、完成加密密钥协商等。如果仅有Wi-Fi而蜂窝数据关闭,且Wi-Fi环境无法连通WhatsApp服务器,那么验证过程将陷入停滞。因此,在中国场景下,开启蜂窝数据(即建立PDP数据通路)是WhatsApp客户端尝试绕过Wi-Fi限制、直接通过移动网络进行验证通信的前提faq.whatsapp.comsohu.com。值得一提的是,PDP Context的建立也表明手机在运营商网络上处于活跃状态,这对于某些验证机制(比如后述的闪信/闪呼)来说至关重要。
IMSI与MSISDN: IMSI(国际移动用户标识)和MSISDN(移动用户号码,即手机号码)是运营商网络中两个密切相关但不同的标识。IMSI是存储在SIM卡上的一串唯一数字,用于在移动网络中标识用户身份netmanias.com。当手机接入网络时,它向运营商提供IMSI以进行鉴权,运营商据此知道“是哪张SIM”的请求netmanias.com。而MSISDN则是我们平常说的手机号,用于在语音通话和短信路由中定位用户,也存储在运营商的HLR/HSS数据库中netmanias.com。运营商通过IMSI<->MSISDN的对应关系,将来自全球的短信/电话正确路由到用户手机上。WhatsApp的验证短信或电话本质上就是通过目标号码(MSISDN)寻找所属运营商网络,由该网络根据IMSI定位用户终端。一般情况下,WhatsApp应用并不直接接触IMSI这种信息,因为IMSI属于运营商网络的内部标识。然而,IMSI的存在仍然对安全产生影响。例如,**SIM卡交换(SIM Swap)**欺诈发生时,攻击者获得了受害者号码的新SIM卡,新SIM卡会有不同的IMSI,但MSISDN保持原号码不变。运营商会将原号码映射到新的IMSI,这样验证码短信就发送到了攻击者手中的SIM上。对WhatsApp而言,除非有机制检测IMSI变动,否则无法察觉用户号码背后的SIM已被盗换。部分应用在检测到SIM变化时会提示用户重新验证,这需要读取设备的IMSI信息进行比对。然而,在现代智能手机中,获取IMSI通常需要特殊权限,WhatsApp并未明确说明它有此类检测。因此,从WhatsApp角度,IMSI更多是网络侧的概念,但它提醒我们:电信级身份验证依赖于SIM的有效性。只有当正确的IMSI在网络注册、并建立了PDP数据上下文时,WhatsApp的后台服务才能确认该SIM对应的号码目前“在线”,进而可靠地发送验证信号(短信或电话)到该设备。
移动网络的信号辅助验证: 有观点认为,一些OTT应用可能利用移动网络提供的附加服务来辅助号码验证。例如,某些运营商提供号码快速验证API,当应用检测到设备在移动数据网络中时,可以向特定地址发起请求,由运营商返回当前设备的号码信息(通常通过已经建立的PDP通道)。Google等公司在部分国家与运营商合作过类似服务,实现用户免输入验证码自动完成验证。但就WhatsApp而言,没有公开证据表明其使用了运营商提供的自动号码识别API。即便如此,WhatsApp鼓励用户保持移动网络在线的做法,隐含的意义之一可能是:当手机处于蜂窝网络且数据畅通时,验证码通过率和验证成功率都会显著提升。这既包括了物理层面短信、电话能否送达,也涵盖了数据层面应用和服务器能否互通。
Flash Call机制:WhatsApp验证的新方案
针对传统SMS验证码容易被拦截、延迟以及用户体验不佳的问题,WhatsApp近年来引入了一种Flash Call(闪呼)验证机制fossbytes.com。所谓闪呼,即应用在用户验证阶段向用户的手机号发起一个非常短暂的来电:用户无需真正接听,WhatsApp会自动结束这通电话,并根据通话记录来确认是否拨通fossbytes.com。
原理与流程: 当用户选择使用闪呼验证(目前主要在Android设备上可用),WhatsApp会请求权限访问用户的通话记录fossbytes.com。随后应用拨打用户的号码,一般是一个预先设定的特定号码或号码段。由于WhatsApp后台知道它拨出的号码及通话ID,只要该未接来电出现在用户手机的通话日志中,应用即可读取并匹配最后一通来电的号码是否符合验证要求,从而确认用户持有这个号码fossbytes.com。整个过程用户无需手动输入验证码,验证通话在数秒内完成。相比6位数字短信验证码需要用户在短信和应用间切换输入,闪呼方式更加快捷无缝fossbytes.com。
优缺点分析: 闪呼验证的优势在于速度快且避免了SMS可能的延迟或拦截。一些分析指出闪呼将成为取代SMS OTP(一次性密码)的新趋势,Juniper Research预测2022年用于验证的闪呼次数将从2021年的六千万猛增到五十亿次subex.comglobaltelcoconsult.com。对于WhatsApp这样全球用户庞大的应用,闪呼可以节约大量SMS网关费用,并绕开部分运营商对国际SMS的限制。然而,闪呼也有局限:fossbytes.com首先,iOS设备由于系统安全限制,应用无法访问通话记录,因此iPhone上无法使用闪呼验证fossbytes.com。这意味着苹果用户仍需使用传统短信验证码。其次,为实现自动匹配来电号码,用户必须授予读取通话记录的权限,这在隐私上引发一些担忧fossbytes.comfossbytes.com。WhatsApp声称不会将通话记录用于验证以外的用途,号码匹配也在本地完成fossbytes.com,但考虑到母公司Meta的隐私争议,部分用户依然顾虑。第三,闪呼验证依赖语音通话路线,同样受制于电信网络质量。如果用户所处网络无法接通国际来电(比如被运营商拦截境外短振铃电话),闪呼也无法成功。此外,从运营商角度看,闪呼绕过了A2P短信计费,可能侵蚀短信营收,一些运营商开始研究识别闪呼流量的策略wholesale.orange.com。总体而言,闪呼机制体现了WhatsApp希望减轻对短信依赖的努力,它在许多国家提升了验证体验,但在中国等特殊环境,其效果仍取决于本地语音网络的开放程度。值得注意的是,中国运营商对于境外电话,尤其是这种**“零响铃”未接来电**也有防范措施,中国电信和联通用户就被建议如需接收海外来电验证,应联系客服确保未拦截海外来电hqsmartcloud.com。因此,即便WhatsApp支持闪呼,中国用户若未开启移动语音漫游或运营商许可,仍然难以通过此途径完成验证。
与SIM Swap安全性的关系: 从安全角度看,闪呼并未实质提升抵御SIM交换攻击的能力。如果攻击者成功将受害者的号码转移至自己的SIM卡上(获取新IMSI),那么无论验证码以短信还是闪呼方式发送,都会到达攻击者设备。闪呼机制能防御的是部分恶意拦截短信的行为(如恶意网关或木马读取短信),但对社工换卡没有太大帮助。WhatsApp早已提供两步验证(即设置6位PIN码)供用户自行启用,以防号码被他人重新注册时需要额外密码。然而大量用户未开启该功能。因此,闪呼更多是从用户体验和成本出发的改良,而非针对高级别攻击的防护机制。正如前文所述,真正要防御SIM Swap和SS7漏洞等系统性风险,依赖运营商的号码验证本身就是薄弱环节,需要引入更高级的身份认证手段。
SIM卡交换攻击的风险与运营商信任问题
WhatsApp和Telegram一类基于手机号认证的应用普遍面临一个安全挑战:手机号码本身并非绝对安全的身份凭证。攻击者可以通过一系列手段取得用户的号码控制权,其中SIM交换(SIM Swap)是近年高发的欺诈手法。SIM Swap通常由不法分子冒充用户,诱骗或贿赂运营商客服将目标号码的服务转移到攻击者的新SIM卡上keepnetlabs.com。一旦成功,所有发往该号码的短信和电话都转由攻击者接收,原机主的SIM卡失效。对于依赖短信/电话验证的应用来说,这意味着攻击者可以轻易获取验证码,从而重置账户并登录。近年来全球SIM Swap案件呈上升趋势,许多在线服务的账号被此攻破rte.ie。
WhatsApp并非未知晓此风险。事实上,WhatsApp在其帮助中心和安全博客中多次提醒用户开启两步验证PIN,并强调绝不向他人透露短信验证码。然而,从系统设计上讲,WhatsApp仍将信任根基放在运营商发送到用户手机的那串数字验证码上。一旦运营商端的安全被绕过(无论是内部员工作恶、社工欺诈,还是SS7网络被黑客利用securityaffairs.com),WhatsApp本身无法辨别验证码接收者是否是真正的用户。正如安全研究所Positive Technologies指出的那样,目前主要的即时通讯服务(包括WhatsApp和Telegram)依赖SMS作为主要验证机制,这使得黑客能够通过攻击电信信令网络来接管用户账户securityaffairs.com。换言之,WhatsApp被迫信任每一个参与短信/电话路由的运营商,但这个信任链条上任何薄弱环节都可能遭到利用securityaffairs.com。例如,在SIM Swap攻击中,运营商本身成为被欺骗的对象;而在SS7定位拦截攻击中,全球互联的电信网成为攻击面。在中国的场景下,虽然主要威胁来自审查而非黑客,但本质上仍是WhatsApp无法完全掌控电信网络这一事实所导致的问题。
应对这些风险,WhatsApp和Telegram等采用了一些弥补措施。除了提供用户自行设定的二次密码,两者也开始探索设备多因子的概念(如后文Telegram部分所述,利用已有登录设备确认新登录)。然而,对绝大多数首次注册或更换设备的用户来说,传统的短信/电话验证仍是唯一途径。这就是为什么在高安全需求的行业中,SMS OTP正逐渐被视为不充分securityaffairs.com。监管机构和安全专家建议对涉敏感操作采用更强验证,如专用身份应用、硬件令牌或生物识别等。WhatsApp作为大众通信工具,目前平衡了易用性与安全性,但其依赖电信运营商的验证模式在像中国这样特殊的环境下,既遇到政策阻碍,也隐藏安全短板。这一点对于决策制定者评估国外通信应用在华风险时,是一个重要考量:任何全球运营商合作机制,在中国境内都可能因为**“最后一公里”由中国运营商执行**而受到影响。无论是被拦截信息还是可能的监控窃听,这些风险都源自于底层通信网的控制权不在应用服务商手中。
Telegram登录机制的比较
作为对比,Telegram的账号登录机制与WhatsApp类似,也以手机号码为主要身份标识,但在具体实现上有一些不同之处。
多设备登录与云端代码: Telegram从设计上支持多设备同时在线(手机、平板、PC等),并将聊天内容储存在云端。这带来的一个直接好处是:当用户在新设备上登录时,Telegram会优先通过已登录的其他设备发送登录验证码。例如,用户尝试在电脑上登录Telegram,Telegram会在用户手机上的Telegram应用里推送一条消息包含登录码,而不是立即发短信accountboy.comaccountboy.com。用户只需在新设备输入从老设备上收到的代码即可完成登录。这种机制确保了只要用户至少有一个设备在线,就几乎不需要依赖运营商短信。当然,如果用户当前只有一部新设备(例如换了手机且旧设备不上线),Telegram才会退而求其次,通过SMS发送验证码到手机号。同时,Telegram也允许用户选择语音电话获取验证码,类似于WhatsApp的语音验证。当用户完全无法收到SMS时(比如在中国这种场景),语音呼叫常常比短信更可靠seatuo.com。
两步验证密码: 与WhatsApp一样,Telegram提供可选的两步验证密码。当启用此功能后,即使拿到短信验证码,仍需输入用户设置的密码才能登录账户quora.com。这对抗SIM Swap等攻击提供了另一层防线。不过需要指出,如果用户忘记了设置的Telegram密码且没有设置信任邮箱,可能会永久失去账号访问,因此开启该功能在中国用户中接受度一般。
登录体验与安全性的取舍: Telegram的登录流程在用户体验上更加灵活。多设备下无需每次都收验证码,提高了便利性。但从安全角度看,这种“信任已有设备”的做法也有隐患:如果用户的某个设备落入他人之手并未及时登出,那么该人有可能利用该设备获取新的登录验证码。因此Telegram会在应用中提供管理活动会话的功能,用户可随时查看和撤销其它设备的登录状态telegram.org。总体而言,Telegram和WhatsApp在初始注册环节同样依赖短信/电话,在这一点上,中国的网络环境对两者影响相似:Telegram在中国同样被全面封锁,需要VPN才能使用,其短信验证码发送也会受到运营商限制。另外,Telegram曾在2015年因恐怖分子利用该平台传递信息而被中国当局重点关注并屏蔽,因此其国内可达性甚至比WhatsApp更低。许多中国用户实际使用Telegram时,通常绑定国外号码或通过海外SIM卡来收取验证码,以绕开国内运营商的限制。
差异总结: 简而言之,Telegram在登录验证机制上的主要优势在于已有会话协助和云端同步。这使得老用户换设备时不依赖国内短信通道即可登录(前提是原设备已登录并可访问)。WhatsApp直到最近才推出多设备功能,但其多设备模式采用的是端到端加密设备链路,需要主手机扫码授权,而非像Telegram那样用账号密码登录其它设备。因此WhatsApp仍然强绑定SIM卡设备,首次注册和更换手机号时逃不开运营商环节。安全方面,两者的SMS验证所面临的系统性风险(如SS7攻击、SIM Swap)并无本质区别,都必须仰仗运营商加强对核心网络的保护,以及用户自身启用附加验证措施securityaffairs.comkeepnetlabs.com。
结论
对于希望在中国使用WhatsApp的用户来说,“开启蜂窝数据”这一要求背后体现的是技术与政策交织的复杂现实。一方面,蜂窝数据承载着WhatsApp与其全球服务器通信的关键信道,在中国的受限网络中提供了相对可靠的出路faq.whatsapp.comsohu.com。另一方面,WhatsApp的号码验证机制深深植根于传统电信体系,必须经由全球运营商的“协作”才能完成用户身份确认securityaffairs.com。而在中国,这种协作受到防火长城和运营商政策的双重阻碍:国际短信被拦截、国际数据被阻断。为克服这些障碍,WhatsApp既采取了工程上的应对(如检测强制Wi-Fi并提示使用移动网络faq.whatsapp.com),也引入了诸如闪呼验证等新方案以减少对短信的依赖fossbytes.com。但从根本上说,只要注册流程离不开手机号码,这种与电信运营商的捆绑关系就无法割舍。由此带来的安全问题(如SIM Swap和信令网络漏洞)在全球范围内敲响警钟securityaffairs.comkeepnetlabs.com。
对于从事安全研究和政策评估的人士,这篇分析揭示了WhatsApp在中国遇到的典型困境:技术系统的全球化与监管环境的本地化冲突。WhatsApp全球统一的验证框架在中国水土不服,不得不通过额外的设置和手段来“曲线救国”。这既包括让用户切换网络、配置VPN等绕过审查,也包括思考未来是否有必要采用更安全独立的验证方式。相比之下,Telegram的机制给出了一种启示:灵活运用多设备和云服务,至少在一定程度上降低对单一短信渠道的依赖。然而,Telegram自身在中国的处境表明,再优雅的技术方案也难以直接对抗高强度的网络封锁。最终,无论是WhatsApp还是Telegram,要想在受限环境下可靠运作,都需要技术与政策的双管齐下:一方面提高验证与登录的安全性和多样性,另一方面寻求运营商和监管层面的理解与配合。
综上所述,WhatsApp要求中国用户开启蜂窝数据并非偶然的臆想,而是其全球运营商合作验证机制在中国受阻后的务实选择。这一要求折射出移动通信应用在跨境运营中面临的挑战,也提醒我们在设计安全策略时必须考虑底层依赖的信任假设。对于个人用户,最实际的建议是在使用此类应用时提前了解并遵循这些特殊设置(如开通国际短信、启用数据漫游),并善用应用自身的安全功能(如两步验证)来保护账户免遭社工和网络攻击keepnetlabs.com。对于监管和运营商,则有必要权衡安全审查与用户便利之间的平衡,在可控范围内为可信的全球服务留出技术通道。在全球通信愈加融合的时代,WhatsApp的中国验证问题或许只是一个缩影,背后涉及的既有网络安全考量,也有数字主权与国际合作的议题,值得持续深入研究和关注。
faq.whatsapp.comfossbytes.comtheguardian.comsecurityaffairs.comsecurityaffairs.comkeepnetlabs.comdatascientest.comnetmanias.comsohu.comsohu.com
-
 @ 0176967e:1e6f471e
2024-07-21 11:28:18
@ 0176967e:1e6f471e
2024-07-21 11:28:18Čo nám prinášajú exotické protokoly ako Nostr, Cashu alebo Reticulum? Šifrovanie, podpisovanie, peer to peer komunikáciu, nové spôsoby šírenia a odmeňovania obsahu.
Ukážeme si kúl appky, ako sa dajú jednotlivé siete prepájať a ako spolu súvisia.
-
 @ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03
@ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ 3bf0c63f:aefa459d
2025-04-25 18:55:52
@ 3bf0c63f:aefa459d
2025-04-25 18:55:52Report of how the money Jack donated to the cause in December 2022 has been misused so far.
Bounties given
March 2025
- Dhalsim: 1,110,540 - Work on Nostr wiki data processing
February 2025
- BOUNTY* NullKotlinDev: 950,480 - Twine RSS reader Nostr integration
- Dhalsim: 2,094,584 - Work on Hypothes.is Nostr fork
- Constant, Biz and J: 11,700,588 - Nostr Special Forces
January 2025
- Constant, Biz and J: 11,610,987 - Nostr Special Forces
- BOUNTY* NullKotlinDev: 843,840 - Feeder RSS reader Nostr integration
- BOUNTY* NullKotlinDev: 797,500 - ReadYou RSS reader Nostr integration
December 2024
- BOUNTY* tijl: 1,679,500 - Nostr integration into RSS readers yarr and miniflux
- Constant, Biz and J: 10,736,166 - Nostr Special Forces
- Thereza: 1,020,000 - Podcast outreach initiative
November 2024
- Constant, Biz and J: 5,422,464 - Nostr Special Forces
October 2024
- Nostrdam: 300,000 - hackathon prize
- Svetski: 5,000,000 - Latin America Nostr events contribution
- Quentin: 5,000,000 - nostrcheck.me
June 2024
- Darashi: 5,000,000 - maintaining nos.today, searchnos, search.nos.today and other experiments
- Toshiya: 5,000,000 - keeping the NIPs repo clean and other stuff
May 2024
- James: 3,500,000 - https://github.com/jamesmagoo/nostr-writer
- Yakihonne: 5,000,000 - spreading the word in Asia
- Dashu: 9,000,000 - https://github.com/haorendashu/nostrmo
February 2024
- Viktor: 5,000,000 - https://github.com/viktorvsk/saltivka and https://github.com/viktorvsk/knowstr
- Eric T: 5,000,000 - https://github.com/tcheeric/nostr-java
- Semisol: 5,000,000 - https://relay.noswhere.com/ and https://hist.nostr.land relays
- Sebastian: 5,000,000 - Drupal stuff and nostr-php work
- tijl: 5,000,000 - Cloudron, Yunohost and Fraidycat attempts
- Null Kotlin Dev: 5,000,000 - AntennaPod attempt
December 2023
- hzrd: 5,000,000 - Nostrudel
- awayuki: 5,000,000 - NOSTOPUS illustrations
- bera: 5,000,000 - getwired.app
- Chris: 5,000,000 - resolvr.io
- NoGood: 10,000,000 - nostrexplained.com stories
October 2023
- SnowCait: 5,000,000 - https://nostter.vercel.app/ and other tools
- Shaun: 10,000,000 - https://yakihonne.com/, events and work on Nostr awareness
- Derek Ross: 10,000,000 - spreading the word around the world
- fmar: 5,000,000 - https://github.com/frnandu/yana
- The Nostr Report: 2,500,000 - curating stuff
- james magoo: 2,500,000 - the Obsidian plugin: https://github.com/jamesmagoo/nostr-writer
August 2023
- Paul Miller: 5,000,000 - JS libraries and cryptography-related work
- BOUNTY tijl: 5,000,000 - https://github.com/github-tijlxyz/wikinostr
- gzuus: 5,000,000 - https://nostree.me/
July 2023
- syusui-s: 5,000,000 - rabbit, a tweetdeck-like Nostr client: https://syusui-s.github.io/rabbit/
- kojira: 5,000,000 - Nostr fanzine, Nostr discussion groups in Japan, hardware experiments
- darashi: 5,000,000 - https://github.com/darashi/nos.today, https://github.com/darashi/searchnos, https://github.com/darashi/murasaki
- jeff g: 5,000,000 - https://nostr.how and https://listr.lol, plus other contributions
- cloud fodder: 5,000,000 - https://nostr1.com (open-source)
- utxo.one: 5,000,000 - https://relaying.io (open-source)
- Max DeMarco: 10,269,507 - https://www.youtube.com/watch?v=aA-jiiepOrE
- BOUNTY optout21: 1,000,000 - https://github.com/optout21/nip41-proto0 (proposed nip41 CLI)
- BOUNTY Leo: 1,000,000 - https://github.com/leo-lox/camelus (an old relay thing I forgot exactly)
June 2023
- BOUNTY: Sepher: 2,000,000 - a webapp for making lists of anything: https://pinstr.app/
- BOUNTY: Kieran: 10,000,000 - implement gossip algorithm on Snort, implement all the other nice things: manual relay selection, following hints etc.
- Mattn: 5,000,000 - a myriad of projects and contributions to Nostr projects: https://github.com/search?q=owner%3Amattn+nostr&type=code
- BOUNTY: lynn: 2,000,000 - a simple and clean git nostr CLI written in Go, compatible with William's original git-nostr-tools; and implement threaded comments on https://github.com/fiatjaf/nocomment.
- Jack Chakany: 5,000,000 - https://github.com/jacany/nblog
- BOUNTY: Dan: 2,000,000 - https://metadata.nostr.com/
April 2023
- BOUNTY: Blake Jakopovic: 590,000 - event deleter tool, NIP dependency organization
- BOUNTY: koalasat: 1,000,000 - display relays
- BOUNTY: Mike Dilger: 4,000,000 - display relays, follow event hints (Gossip)
- BOUNTY: kaiwolfram: 5,000,000 - display relays, follow event hints, choose relays to publish (Nozzle)
- Daniele Tonon: 3,000,000 - Gossip
- bu5hm4nn: 3,000,000 - Gossip
- BOUNTY: hodlbod: 4,000,000 - display relays, follow event hints
March 2023
- Doug Hoyte: 5,000,000 sats - https://github.com/hoytech/strfry
- Alex Gleason: 5,000,000 sats - https://gitlab.com/soapbox-pub/mostr
- verbiricha: 5,000,000 sats - https://badges.page/, https://habla.news/
- talvasconcelos: 5,000,000 sats - https://migrate.nostr.com, https://read.nostr.com, https://write.nostr.com/
- BOUNTY: Gossip model: 5,000,000 - https://camelus.app/
- BOUNTY: Gossip model: 5,000,000 - https://github.com/kaiwolfram/Nozzle
- BOUNTY: Bounty Manager: 5,000,000 - https://nostrbounties.com/
February 2023
- styppo: 5,000,000 sats - https://hamstr.to/
- sandwich: 5,000,000 sats - https://nostr.watch/
- BOUNTY: Relay-centric client designs: 5,000,000 sats https://bountsr.org/design/2023/01/26/relay-based-design.html
- BOUNTY: Gossip model on https://coracle.social/: 5,000,000 sats
- Nostrovia Podcast: 3,000,000 sats - https://nostrovia.org/
- BOUNTY: Nostr-Desk / Monstr: 5,000,000 sats - https://github.com/alemmens/monstr
- Mike Dilger: 5,000,000 sats - https://github.com/mikedilger/gossip
January 2023
- ismyhc: 5,000,000 sats - https://github.com/Galaxoid-Labs/Seer
- Martti Malmi: 5,000,000 sats - https://iris.to/
- Carlos Autonomous: 5,000,000 sats - https://github.com/BrightonBTC/bija
- Koala Sat: 5,000,000 - https://github.com/KoalaSat/nostros
- Vitor Pamplona: 5,000,000 - https://github.com/vitorpamplona/amethyst
- Cameri: 5,000,000 - https://github.com/Cameri/nostream
December 2022
- William Casarin: 7 BTC - splitting the fund
- pseudozach: 5,000,000 sats - https://nostr.directory/
- Sondre Bjellas: 5,000,000 sats - https://notes.blockcore.net/
- Null Dev: 5,000,000 sats - https://github.com/KotlinGeekDev/Nosky
- Blake Jakopovic: 5,000,000 sats - https://github.com/blakejakopovic/nostcat, https://github.com/blakejakopovic/nostreq and https://github.com/blakejakopovic/NostrEventPlayground
-
 @ 866e0139:6a9334e5
2025-05-22 06:46:34
@ 866e0139:6a9334e5
2025-05-22 06:46:34Autor: Jana Moava. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie auch in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Zwei Worte nur braucht man – und die Sache ist klar. Jeder gebildete Russe kennt diese Worte: sie stammen aus dem XIX. Jahrhundert, als Nikolaus I. die Krim-Kampagne begann und das Zarenreich nach üblen Querelen ganz Europa und die Türkei zum Gegner hatte - allen voran die Herrscher der Weltmeere: das British Empire mit Queen Victoria. Der historische Ausdruck anglitschanka gadit (locker übersetzt: die Engländerin macht Shit) besitzt bis heute verdeckte politische Sprengkraft und ist seit Ende Februar 2022 in Russland wieder populär. Wer auch immer der Urheber dieser im Original durchaus diskreten Benennung des Fäkalvorgangs war: der Ausdruck steht für ernste Konflikte mit dem Englisch sprechenden Westen, dem Erzfeind.
Ein kurzer Blick in die Geschichte mag dies erläutern: Fast alle westlichen Historiker benennen als Auslöser des Krimkrieges Mitte des IX. Jahrhunderts die Verteidigung der russisch-orthodoxen Kirche und deren Zugang zur Kreuzkirche in Jerusalem. Es wird vom letzten Kreuzzug u.a. geschrieben. Das ist eine höchst einseitige Interpretation, denn es ging Nikolaus I. vor allem um den Zugang zum einzigen dauerhaft eisfreien Hafen Russlands im Schwarzen Meer, durch die Meeresenge der Dardanellen ins Mittelmeer. Das ist verständlich, war doch die Eroberung der Krim ab 1783 unter seiner Großmutter Katharina II. aus eben diesem Grunde erfolgt. Damals schon wurde der Hafen Sewastopol zum Stützpunkt der russischen Flotte ausgebaut.
Ende 1825, nach dem plötzlichen Tod des ältesten Bruders Alexander I., war Nikolaus von seiner Erziehung her auf eine Regentschaft ganz und gar nicht vorbereitet gewesen, doch herrschte er dreißig Jahre lang nicht nur über das russische Reich, sondern auch über Finnland und das damalige Königreich Polen unter russischem Protektorat. Nikolaus I. zeichnete sich von Beginn an durch Gewaltmaßnahmen aus: Als ihm im Dezember (russ. dekabr)1825 eine Gruppe sehr gebildeter, freiheitsliebender junger Adligen aus besten Familien den Eid verweigerte (dies zog als Dekabristenaufstand in die Geschichte ein), ließ er fünf der Rebellen hängen, die anderen schickte er in Fußfesseln nach Sibirien in die Bergwerke. Er gründete die berüchtigte Geheimpolizei Dritte Abteilung, ließ Privatbriefe des Dichters Puschkin öffnen (obwohl dieser „in seiner Gnade stand“) und Historikern ist Nikolaus I. als Gendarm Europas bekannt. Im russischen Volk aber nannte man ihn kurz und bündig: *Nicki Knüppel aus dem Sack (Nikolaschka palkin). *
Leo Tolstoj beschrieb diesen Zaren in seinen Erzählungen über die Kriege im Kaukasus (Hadschi Murat) als feist und fett, mit leblosen, trüben Augen und als berüchtigten Frauenjäger. Tolstoj war es auch, der als junger Teilnehmer im Krimkrieg drei Erzählungen schrieb: Sewastopol im Dezember 1854, im Mai 1855 und im August 1855. Nachdem das British Empire unter Queen Victoria Russland den Krieg erklärt hatte (in Koalition mit Frankreich und Piemont-Sardinien als Schutzmacht des Osmanischen Reiches), entstand der Ausdruck anglitschanka gadit – die Engländerin macht Shit. Bis heute findet man dazu drastische Illustrationen im Netz…
Noch bevor russische Truppen Ende Februar 2022 in die Ukraine marschierten, lebte dieser Ausdruck in Russland wieder auf. Wer hierzulande Interesse an der Wahrheit hat, kann deutliche Parallelen zur damaligen politischen Lage entdecken, auch in Bezug auf die Verhaltensweisen des derzeitigen russischen Staatschefs und des historischen Nicki Knüppel aus dem Sack. Obwohl der amtierende durchaus Anerkennung verdient hat, denn nach dem Zusammenbruch der Sowjetunion in den 1990er Jahren unter Jelzin stellte er die Staatlich-keit des verlotterten, hungernden Landes wieder her und trieb den wirtschaftlichen Aufbau voran. Davon kann ich zeugen, lebte ich doch von 1992 – 2008 vor Ort.
Sicher - heute ist längst bekannt, daß die bereits Ende März 2022 in Istanbul laufenden Friedensverhandlungen zwischen Russland und der Ukraine vom britischen Premier und im Namen des US Präsidenten boykottiert wurden. Daniel Ruch, Schweizer Botschafter a.D., sprach gar von Sabotage! Der deutsche General a. D. Harald Kujat kommentierte damals mit den Worten: „Seit April 2022 gehen alle Kriegsopfer in der Ukraine auf das Konto des Westens!“ Der Ausdruck anglitschanka gadit ist seitdem in Russland wieder geläufig. Nun, brandaktuell, treffen sich die Kriegsparteien wieder in Istanbul: Ausgang ungewiss. Doch wird inzwischen auch von einzelnen westlichen Politikern anerkannt, dass Russland eine neutrale Pufferzone zu den Nato-Staaten verlangt und braucht.
Wenn hierzulande gemutmaßt wird, alle Russen würden den Ukraine-Krieg bejahen, so sollte man zur Kenntnis nehmen, dass derartige Aussagen kaum die wirkliche Überzeugung wiedergeben. Seit den Repressionen unter Stalin, seit in jeder zweiten Familie nahe Angehörige im GULAG einsaßen und umkamen und darüber Jahrzehnte lang geschwiegen werden musste, ist der Wahrheitsgehalt öffentlicher Umfragen getrost zu bezweifeln. Hat man hier etwa vergessen, dass seit 2011 auf eine mächtig wachsende zivile Protestbewegung und riesige Demonstrationen in russischen Großstädten immer schärfere Aktionen von Seiten des Staates erfolgten? Dass Knüppel auf Köpfe und Leiber prasselten, wie zur Zeit Nickis I., und der Polizeiapparat derart wuchs, dass heute das Verhältnis von Bürger und Silowiki (Vertreter der Gewalt)1:1 steht?
Offenbar weiß man hier nicht, dass schon Anfang 2022 von Mitarbeitern in jeder staatlich finanzierten Institution, ob im Bereich von Kultur, Wissenschaft, Forschung oder Lehre die schriftliche Zustimmung zur Spezialoperation mit der Ukraine eingefordert wurde! Eine Weigerung hatte den Verlust des Arbeitsplatzes zur Folge, egal welches Renommée oder welchen Rang der Betroffene besaß! Manche Leiter von staatlichen Institutionen zeigten dabei gehöriges Geschick und zeichneten für alle; andere (z.B. staatliche Theater) riefen jeden Mitarbeiter ins Kontor. Nur wenige Personen, die unter dem persönlichem Schutz des Präsidenten standen, konnten sich dieser Zustimmung zum Krieg entziehen. Wissenschaftler und Künstler emigrierten zuhauf. Berlin ist voll mit Geflohenen aus jenem Land, das kriegerisch ins Bruderland einmarschierte! Aber kann denn jeder emigrieren? Die Alten, Familien mit Kindern? Mit guten Freunden, die dort blieben, ist eine Kommunikation nur verschlüsselt möglich, in Nachrichten wie: die Feuer der Inquisition brennen (jeder, der von der offiziellen Doktrin abweicht, ist gefährdet), Ratten verbreiten Krankheiten bezieht sich auf Denunziationen, die in jeder Diktatur aufblühen, wenn sich jemand dem Schussfeld entziehen möchte und im vorauseilenden Gehorsam den Nachbarn anzeigt. Kennen wir das nicht noch aus unseren hitlerdeutschen 1930er Jahren?!
Je mehr im Reich aller Russen in den letzten Jahren von oben geknebelt und geknüppelt wurde, desto mehr Denunziationen griffen um sich. Junge Menschen, die auf Facebook gegen den Krieg posteten, wurden verhaftet. Seit 2023 sitzen u.a. zwei junge russische Theaterfrauen aufgrund der üblen Denunziation eines Kollegen hinter Gittern. Die Inszenierung der Regisseurin Zhenja Berkowitsch und der Autorin Swetlana Petritschuk erhielt Ende 2022 den höchsten Theaterpreis von ganz Russland, die Goldene Maske. Das Stück Finist (Phönix), klarer Falke ist nach dem Motiv eines russischen Märchens geschrieben, fußt aber auf dokumentarischem Material: es verhandelt die Versuchung junger Frauen, auf Islamisten hereinzufallen und sie aus Frust und falsch verstandener Solidarität zu heiraten. Die Anklage hat den Spieß genau umgedreht: Autorin und Regisseurin wurden des Terrorismus beschuldigt! Das Rechtssystem im Land scheint heute noch vergleichbar mit jenem, das Alexander Puschkin vor über 200 Jahren in seiner Erzählung Dubrowski authentisch beschrieb: Wer die Macht hat, regelt das Recht. Man kann die Erzählung des russischen Robin Hood auch deutsch nachlesen (leider, leider hat Puschkin sie nicht beendet).
Andere, erbaulichere Elemente aus der Zeit Puschkins, bzw. von Nikolaus I., dienen allerdings als Gegengewicht zum Alltag: seit Ende 2007 finden in Moskau und St. Petersburg jeden Winter nach dem Vorbild der historischen Adelsbälle große gesellschaftliche Events statt: Puschkinball, Wiener Opernball, jetzt nur noch Opernball genannt. Der Nachwuchs aus begüterten Familien lernt alte Tanzschritte und feine Sitten. Fort mit dem sowjetischen Schmuddelimage! Prächtige Kostümbälle werden nun zum Abschluss jedes Schuljahres aufgeboten. In stilisierten Kostümen der Zeit Nikolajs I. bzw. Puschkins tanzen Schuldirektoren, Lehrer und junge Absolventen. Der Drang nach altem Glanz und Größe (oder eine notwendige Kompensation?) spiegelt sich im Volk.
Werfen wir jedoch einen Blick auf einige Geschehnisse in der Ukraine ab 2014, die in unserer Presse immer noch verschwiegen werden: Im Spätsommer 2022 begegnete ich auf Kreta einer Ukrainerin aus der Nordukraine, die wegen des fürchterlichen Nationalismus nach 2014 ihre Heimat verließ. Sie ist nicht die einzige! Ihre Kinder waren erwachsen und zogen nach Polen, sie aber reiste mit einer Freundin weiter Richtung Griechenland, lernte die Sprache, erwarb die Staatsbürgerschaft und ist nun auf Kreta verheiratet.
Natalia erzählte mir, was bei uns kaum zu lesen ist, was jedoch Reporter wie Patrick Baab oder Historiker wie Daniele Ganser schon lange berichtet haben: 2014, als die Bilder der Proteste auf dem Maidan um die Welt gingen, habe die damalige amerikanische Regierung unter Präsident Biden die Vorgänge in Kiew für einen Putsch genutzt: Janukowitsch, der korrupte, doch demokratisch gewählte Präsident der Ukraine wurde gestürzt, die Ereignisse mit Hilfe von Strohmännern und rechten Nationalisten gelenkt, die mit Geld versorgt wurden. Bis es zum Massaker auf dem Maidan kam, als bewaffnete, ihrer Herkunft nach zunächst nicht identifi-zierbare Schützen (es waren v.a. rechte Nationalisten, so der gebürtige Ukrainer und US Bürger Professor N. Petro und Prof. Ivan Katchanovskij) von den Dächern in die Menge schossen.
Im YouTube Kanal Neutrality Studies konnte man am 17.02.2024 hören: Anlässlich des traurigen 10. Jahrestages des Maidan-Massakers, bei dem am 20. Februar 2014 mehr als 100 Menschen durch Scharfschützenfeuer getötet wurden, spreche ich heute mit Ivan Katchanovski, einem ukrainischen (und kanadischen) Politikwissenschaftler an der Univer-sität von Ottawa, der das Massaker detailliert erforscht hat. Letztes Jahr veröffentlichte er das Papier „Die Maidan-Massaker-Prozess und Untersuchungserkenntnisse: Implikationen für den Krieg zwischen der Ukraine und Russland und die Beziehungen“. Kurz gesagt, das Massaker wurde NICHT von den Kräften Victor Janukowytschs begangen, wie in westlichen Medien berichtet, und es gibt schlüssige Beweise dafür, dass die Schützen Teil des ultra-rechten Flügels der Ukraine waren, die dann nach dem Putsch an die Macht kamen. (Link zum Paper).
Wer erinnert sich hierzulande noch daran, dass 2014 im deutschen öffentlichen Fernsehen von Hunter Biden, Sohn des US-Präsidenten berichtet wurde, der durch dubiose Gas- und Ölgeschäfte in der Ukraine auffiel? Dass damals im deutschen Fernsehen auch Bilder von Ukrainern mit SS-Stahlhelmen auftauchten? In einer Arte-Reportage zu Hilfs-transporten im März 2022 aus Polen über die Westukraine konnte der aufmerksame Zu-schauer an fast allen Häusern die tiefroten Banner von Anhängern des verstorbenen, in München begrabenen, faschistischen Stepan Bandera erkennen. Ausgesprochen wurde es nicht.
Die neue Kreterin Natalia sprach auch über eine Amerikanerin ukrainischer Herkunft, die Röntgenärztin Uljana Suprun, die aus den USA als Gesundheitsministerin rekrutiert wurde und unter dem amerikafreundlichen Präsidenten Poroschenko von 2016-2019 diesen Posten innehatte. Was bitte sollte eine Röntgenärztin aus den USA auf dem Ministerposten der Ukraine?! Streit und Skandal umgaben sie fast täglich in der RADA, dem ukrainischen Parlament. Es wurde gemunkelt, sie diene als Feigenblatt bei der Herstellung biologischer Waffen. Material zu ihr ist bis heute auf YouTube zu finden.
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes.
Natalia bezeichnete die ukrainischen Emigrantenkreise in den USA und Kanada zurecht als ultranationalistisch, sie seien Kollaborateure der Nazis bei der Judenvernichtung gewesen und hätten sich nach dem Rückzug der Deutschen rechtzeitig nach Übersee abgesetzt. Das ist wohl bekannt.
Heute ist das Recherchieren der wahren Geschehnisse von 2014 zwar immer noch mühsam, aber die Wahrheit sickert immer mehr durch, zumal auch Exilukrainer dazu geschrieben und öffentlich gesprochen haben. Die Kanäle SaneVox und Neutrality studies liefern unermüdlich weitere Fakten! Im März 2025 klärte der US-Professor Jeffrey Sachs das Europa-Parlament endlich in allen Details über die kriegerischen Machenschaften bestimmter Kreise innerhalb der englischsprechenden Westmächte auf!
Kürzlich war im multipolar-magazin zu lesen, wie erschreckend tief unser eigenes Land bereits in**** den Ukraine-Krieg verwickelt ist: Da hieß es:
*„Kriegsplanung von deutschem Boden“ *
Zwei umfassende Beiträge der „New York Times“ und der Londoner „Times“ belegen, was lange bestritten wurde: die tiefe militärische und strategische Verwicklung von Nato-Mitgliedsstaaten in den Ukraine-Krieg. Demnach wird deren Kriegsbeteiligung seit Jahren vom europäischen Hauptquartier der US-Armee in Wiesbaden koordiniert. Für Deutschland stellen sich damit verfassungsrechtliche Fragen.
Und ein Karsten Montag schrieb ebenda am 25. April 2025:
Mehr als drei Jahre nach Beginn des russisch-ukrainischen Krieges berichten zwei große westliche Tageszeitungen über die tiefgreifende Beteiligung von Nato-Militärs an diesem Konflikt. Den Anfang machte die „New York Times“ (NYT). Unter dem Titel „Die Partnerschaft: Die geheime Geschichte des Krieges in der Ukraine“ erschien Ende März ein umfassender *Artikel, der laut Autor Adam Entous auf 300 Interviews mit Regierungs-, Militär- und Geheim-dienstvertretern in der Ukraine, den Vereinigten Staaten sowie weiteren Nato-Partnern basiert. Es handle sich um die „unerzählte Geschichte“ der „versteckten Rolle“ der USA bei den ukrainischen Militäroperationen. *
Wenige Wochen später veröffentlichte die britische Tageszeitung „The Times“ Anfang April einen ähnlichen Beitrag mit dem Titel „Die unerzählte Geschichte der entscheidenden Rolle der britischen Militärchefs in der Ukraine“. Dieser bestätigt die tiefe Verstrickung der Nato-Staaten in Militäroperationen wie der ukrainischen Offensive 2023. Abweichend vom NYT-Artikel bezeichnet er jedoch die britischen Militärchefs als die „Köpfe“ der „Anti-Putin“-Koalition. Einigkeit herrscht wiederum bei der Frage, wer für den Misserfolg der Operationen verantwortlich ist: Dies sei eindeutig der Ukraine zuzuschreiben. Auch im Times-Beitrag wird auf die besondere Rolle des europäischen US-Hauptquartiers im hessischen Wiesbaden bei der Koordination der Einsätze und den Waffenlieferungen hingewiesen.
Na also! Es gibt unter den aus der Ukraine Geflüchteten hier allerdings eine große Mehrheit, die von diesen Fakten weder etwas wissen, noch wissen wollen. Amerika und die Heimat der Anglitschanka ist für sie das Gelobte Land und wehe, du sprichst darüber, dann wirst du sofort der russischen Propaganda verdächtig. Wie Nicki mittlerweile daheim den Knüppel schwingt, interessiert sie auch nicht.
Wieso wird hier nicht untersucht, wieso wird verschwiegen, dass Alexej Nawalny für einen englischen Dienst arbeitete – woher erhielt er das viele Geld für seine Kampagnen? Wo leben nun seine Witwe und die Kinder? Auf der Insel im nebligen Avalon/ Albion…
Ein letztes Beispiel aus dem Bereich der Kultur zum Verständnis des leider so aktuellen Ausdrucks Die Engländerin macht Shit: Anfang 2024 wurde im staatlichen Sender ONE (ARD) eine Serie der BBC zu frühen Erzählungen von Michail Bulgakow ausgestrahlt:** Aufzeichnungen eines jungen Arztes. Die BBC verhunzte den in Kiew geborenen Arzt und weltberühmten Autor derart, dass dem Zuschauer schlecht wurde: Mit dem Titel A Young Doctor‘s Notebook verfilmte sie Bulgakows frühe Erzählungen über die Nöte eines jungen Arztes in der bettelarmen sowjetrussischen Provinz in den 1920er Jahren hypernaturalistisch, blut-, dreck- und eitertriefend. Pseudokyrillische Titel und Balalaika Geklimper begleiteten das Leiden von schwer traumatisierten Menschen im russischen Bürgerkrieg oder Abscheulichkeiten, wie das Amputieren eines Mädchenbeines mit einer Baumsäge - ausgestrahlt vom 1. Deutschen Fernsehen! Michail Bulgakow hätte sich im Grabe umgedreht.
Als Autor beherrschte Bulgakow die Kunst der Groteske ebenso wie hochlyrische Schilderungen. Seine Prosa und seine Theaterstücke aber wurden Zeit seines Lebens von der Sowjetmacht verstümmelt - und post mortem auch von seinen ukrainischen Landsleuten: sein schönes Museum, das ehemalige Domizil der Familie Bulgakow in Kiew am Andrejew-Steig, das mit seinem ersten Roman Die weiße Garde (Kiew vor 100 Jahren im Strudel auch ultranationalistischer Strömungen) und der berühmten Dramatisierung Die Tage der Turbins in die große Literatur einzog, dieses Museum wurde abgewickelt und geschlossen, weil Bulgakow angeblich schlecht über die Ukraine geschrieben hätte!
Ein Glück jedoch, dass die bedeutenden Werke Bulgakows seit nun drei Dekaden von russischsprachigen Philologen beharrlich in ihrer ursprünglichen Fassung wieder hergestellt wurden. Seine großen Romane Die weiße Garde und Meister und Margarita seien in der hervorragenden deutschen Übersetzung von Alexander Nitzberg jedem Interessierten ans Herz gelegt!
Die obigen Ausführungen sind keinesfalls eine Rechtfertigung des Krieges, es geht vielmehr um Hintergründe, Fakten und Machenschaften, die in der Regel bis heute bei uns verschwiegen werden! Obwohl es nun sonnenklar und öffentlich ist, dass bestimmte Inter-essengruppen der englischsprachigen Westmächte die hochgefährliche Konfrontationspolitik mit Russland zu verantworten haben: die Engländerin macht Shit…Und wir? Wir schweigen, glauben der immer noch laufenden Propaganda und wehren uns nicht gegen diese üble Russenphobie?! Ich erinnere mich noch lebhaft an die Nachkriegszeit im Ruhrgebiet, als der Ton ruppig war und Dreck und Trümmer unsere Sicht beherrschten. Auch uns kleinen Kindern gegenüber wurde von den bösen Russen gesprochen, als hätten diese unser Land überfallen.
Ja – es waren viele Geflüchtete aus dem Osten hier gestrandet, und diese hatten Unsägliches hinter sich. Lew Kopelew, der den Einmarsch der Roten Armee in Ostpreußen miterlebte und Gräuel vergebens zu verhindern suchte, wurde noch im April 1945 verhaftet und wegen Mitleid mit dem Feind zu 10 Jahren Lager verurteilt. Viele Jahre später erschienen seine Erinnerungen Aufbewahren für alle Zeit – auch auf Deutsch. Über die mindestens 27 Mio Opfer in der damaligen Sowjetunion und über die deutschen Aggressoren, die damals mit Mord und Raub die bösen Russen, sowjetische Zivilisten überfielen, wurde in den 1950er Jahren, im zerbombten und dreckigen Pott kein einziges Wort verloren. Der Spieß wurde einfach umgedreht. Von der Blockade Leningrads erfuhr ich erst als Erwachsene, anno 1974, als Austauschstudentin vor Ort.
Exakt vor 10 Jahren wurde es jedoch möglich – herzlichen Dank der damaligen stell-vertretenden tatarischen Kulturministerin Frau Irada Ayupova! – mein dokumentarisches Antikriegsstück mit Schicksalen von Kriegskindern – sowjetischen, jüdischen, deutschen – in Kasan, der Hauptstadt von Tatarstan, zweisprachig auf die Bühne des dortigen Jugendtheaters zu bringen. Wir spielten 15 Vorstellungen und einige tausend Jugendliche im Saal verstummten und verstanden, dass Krieg furchtbar ist. Hier und heute will leider kein Theater das Stück umsetzen…
Wir Menschen brauchen Frieden und keine Aufrüstung für neue Kriege! Der gute alte Aischylos schrieb einst in seinem Stück Die Perser: Wahrheit ist das erste Opfer eines Krieges. Leider ist dies immer noch genauso aktuell wie damals. Pfui Teufel!
Jana Moava (Pseudonym) ist Journalistin, Dozentin und arbeitete für große Zeitungen als Korrespondentin.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ a39d19ec:3d88f61e
2025-04-22 12:44:42
@ a39d19ec:3d88f61e
2025-04-22 12:44:42Die Debatte um Migration, Grenzsicherung und Abschiebungen wird in Deutschland meist emotional geführt. Wer fordert, dass illegale Einwanderer abgeschoben werden, sieht sich nicht selten dem Vorwurf des Rassismus ausgesetzt. Doch dieser Vorwurf ist nicht nur sachlich unbegründet, sondern verkehrt die Realität ins Gegenteil: Tatsächlich sind es gerade diejenigen, die hinter jeder Forderung nach Rechtssicherheit eine rassistische Motivation vermuten, die selbst in erster Linie nach Hautfarbe, Herkunft oder Nationalität urteilen.
Das Recht steht über Emotionen
Deutschland ist ein Rechtsstaat. Das bedeutet, dass Regeln nicht nach Bauchgefühl oder politischer Stimmungslage ausgelegt werden können, sondern auf klaren gesetzlichen Grundlagen beruhen müssen. Einer dieser Grundsätze ist in Artikel 16a des Grundgesetzes verankert. Dort heißt es:
„Auf Absatz 1 [Asylrecht] kann sich nicht berufen, wer aus einem Mitgliedstaat der Europäischen Gemeinschaften oder aus einem anderen Drittstaat einreist, in dem die Anwendung des Abkommens über die Rechtsstellung der Flüchtlinge und der Europäischen Menschenrechtskonvention sichergestellt ist.“
Das bedeutet, dass jeder, der über sichere Drittstaaten nach Deutschland einreist, keinen Anspruch auf Asyl hat. Wer dennoch bleibt, hält sich illegal im Land auf und unterliegt den geltenden Regelungen zur Rückführung. Die Forderung nach Abschiebungen ist daher nichts anderes als die Forderung nach der Einhaltung von Recht und Gesetz.
Die Umkehrung des Rassismusbegriffs
Wer einerseits behauptet, dass das deutsche Asyl- und Aufenthaltsrecht strikt durchgesetzt werden soll, und andererseits nicht nach Herkunft oder Hautfarbe unterscheidet, handelt wertneutral. Diejenigen jedoch, die in einer solchen Forderung nach Rechtsstaatlichkeit einen rassistischen Unterton sehen, projizieren ihre eigenen Denkmuster auf andere: Sie unterstellen, dass die Debatte ausschließlich entlang ethnischer, rassistischer oder nationaler Kriterien geführt wird – und genau das ist eine rassistische Denkweise.
Jemand, der illegale Einwanderung kritisiert, tut dies nicht, weil ihn die Herkunft der Menschen interessiert, sondern weil er den Rechtsstaat respektiert. Hingegen erkennt jemand, der hinter dieser Kritik Rassismus wittert, offenbar in erster Linie die „Rasse“ oder Herkunft der betreffenden Personen und reduziert sie darauf.
Finanzielle Belastung statt ideologischer Debatte
Neben der rechtlichen gibt es auch eine ökonomische Komponente. Der deutsche Wohlfahrtsstaat basiert auf einem Solidarprinzip: Die Bürger zahlen in das System ein, um sich gegenseitig in schwierigen Zeiten zu unterstützen. Dieser Wohlstand wurde über Generationen hinweg von denjenigen erarbeitet, die hier seit langem leben. Die Priorität liegt daher darauf, die vorhandenen Mittel zuerst unter denjenigen zu verteilen, die durch Steuern, Sozialabgaben und Arbeit zum Erhalt dieses Systems beitragen – nicht unter denen, die sich durch illegale Einreise und fehlende wirtschaftliche Eigenleistung in das System begeben.
Das ist keine ideologische Frage, sondern eine rein wirtschaftliche Abwägung. Ein Sozialsystem kann nur dann nachhaltig funktionieren, wenn es nicht unbegrenzt belastet wird. Würde Deutschland keine klaren Regeln zur Einwanderung und Abschiebung haben, würde dies unweigerlich zur Überlastung des Sozialstaates führen – mit negativen Konsequenzen für alle.
Sozialpatriotismus
Ein weiterer wichtiger Aspekt ist der Schutz der Arbeitsleistung jener Generationen, die Deutschland nach dem Zweiten Weltkrieg mühsam wieder aufgebaut haben. Während oft betont wird, dass die Deutschen moralisch kein Erbe aus der Zeit vor 1945 beanspruchen dürfen – außer der Verantwortung für den Holocaust –, ist es umso bedeutsamer, das neue Erbe nach 1945 zu respektieren, das auf Fleiß, Disziplin und harter Arbeit beruht. Der Wiederaufbau war eine kollektive Leistung deutscher Menschen, deren Früchte nicht bedenkenlos verteilt werden dürfen, sondern vorrangig denjenigen zugutekommen sollten, die dieses Fundament mitgeschaffen oder es über Generationen mitgetragen haben.
Rechtstaatlichkeit ist nicht verhandelbar
Wer sich für eine konsequente Abschiebepraxis ausspricht, tut dies nicht aus rassistischen Motiven, sondern aus Respekt vor der Rechtsstaatlichkeit und den wirtschaftlichen Grundlagen des Landes. Der Vorwurf des Rassismus in diesem Kontext ist daher nicht nur falsch, sondern entlarvt eine selektive Wahrnehmung nach rassistischen Merkmalen bei denjenigen, die ihn erheben.
-
 @ 2b998b04:86727e47
2025-05-22 02:45:34
@ 2b998b04:86727e47
2025-05-22 02:45:34I recently released my first open-source tool:\ 👉 nostr-signal-filter
It fetches and formats your latest top-level Nostr note or long-form article, cleans up any embedded links using TinyURL, and outputs a clean version ready for reposting to:
-
LinkedIn
-
Facebook
-
X / Twitter
⚙️ Built for Simplicity
The stack is intentionally minimal:
-
Python + WebSockets + Bech32
-
TinyURL API for link shortening
-
Dockerized CLI usage:
bashCopyEdit
docker run --rm -e PUBKEY=npub1yourpubkeyhere nostr-fetcher > latest.mdFrom idea to working repo took under 3 hours — including debugging, Docker tweaks, README cleanup, and tagging a clean release.\ \ This most certainly would have taken much longer if I had done this all without ChatGPTs' help.\ \ 🖼️ Example Output (
latest.md)textCopyEdit
🕒 2025-05-20 22:24:17 📄 Note (originally posted on Nostr/primal.net) --- 🚨 New long-form drop: AI Isn’t Magic. It’s Engineering. How I use ChatGPT like any other tool in the stack — with iteration, discernment, and real output. Read it here: https://tinyurl.com/ynv7jq6g ⚡ Zaps appreciated if it resonates. --- 🔗 View on Nostr: https://tinyurl.com/yobvaxkx
🧪 Where I Used It
- ✅ Facebook: clean rendering with preview ->
- ✅ X/Twitter: teaser + link (had to truncate for character limit) ->
https://x.com/AndyGStanton/status/1925045477172773136
🙌 Try It Yourself
If you're publishing on Nostr but still sharing on legacy platforms:
👉 github.com/andrewgstanton/nostr-signal-filter
-
Clean output
-
Easy to run
-
Portable via Docker
All it needs is your
npub.
⚡ Zap Me If You Found This Useful
If this tool saved you time — or if it sparked ideas for your own Nostr publishing stack —\ send a zap my way. I’m always looking to connect with other creators who value signal > noise.
🔗 Zap on Primal -> https://primal.net/andrewgstanton
🔭 Next Features (I’d Love Help With)
-
Archive all notes + articles (not just the latest 50) to
archive.md -
Function to shorten links in any text block
-
Output
post.mdfor any given Nostr event ID (not just latest) -
Optional API integration to post directly to LinkedIn or X
Built with ChatGPT’s help.\ Iterated. Published. Cross-posted.\ That’s proof of work.
-
-
 @ 0176967e:1e6f471e
2024-07-21 11:24:21
@ 0176967e:1e6f471e
2024-07-21 11:24:21Podnikanie je jazyk s "crystal clear" pravidlami. Inštrumentalisti vidia podnikanie staticky, a toto videnie prenášajú na spoločnosť. Preto nás spoločnosť vníma často negatívne. Skutoční podnikatelia sú však "komunikátori".
Jozef Martiniak je zakladateľ AUSEKON - Institute of Austrian School of Economics
-
 @ b83a28b7:35919450
2025-05-16 19:26:56
@ b83a28b7:35919450
2025-05-16 19:26:56This article was originally part of the sermon of Plebchain Radio Episode 111 (May 2, 2025) that nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpqtvqc82mv8cezhax5r34n4muc2c4pgjz8kaye2smj032nngg52clq7fgefr and I did with nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7ct4w35zumn0wd68yvfwvdhk6tcqyzx4h2fv3n9r6hrnjtcrjw43t0g0cmmrgvjmg525rc8hexkxc0kd2rhtk62 and nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpq4wxtsrj7g2jugh70pfkzjln43vgn4p7655pgky9j9w9d75u465pqahkzd0 of the nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcqyqwfvwrccp4j2xsuuvkwg0y6a20637t6f4cc5zzjkx030dkztt7t5hydajn
Listen to the full episode here:
<<https://fountain.fm/episode/Ln9Ej0zCZ5dEwfo8w2Ho>>
Bitcoin has always been a narrative revolution disguised as code. White paper, cypherpunk lore, pizza‑day legends - every block is a paragraph in the world’s most relentless epic. But code alone rarely converts the skeptic; it’s the camp‑fire myth that slips past the prefrontal cortex and shakes hands with the limbic system. People don’t adopt protocols first - they fall in love with protagonists.
Early adopters heard the white‑paper hymn, but most folks need characters first: a pizza‑day dreamer; a mother in a small country, crushed by the cost of remittance; a Warsaw street vendor swapping złoty for sats. When their arcs land, the brain releases a neurochemical OP_RETURN which says, “I belong in this plot.” That’s the sly roundabout orange pill: conviction smuggled inside catharsis.
That’s why, from 22–25 May in Warsaw’s Kinoteka, the Bitcoin Film Fest is loading its reels with rebellion. Each documentary, drama, and animated rabbit‑hole is a stealth wallet, zipping conviction straight into the feels of anyone still clasped within the cold claw of fiat. You come for the plot, you leave checking block heights.
Here's the clip of the sermon from the episode:
nostr:nevent1qvzqqqqqqypzpwp69zm7fewjp0vkp306adnzt7249ytxhz7mq3w5yc629u6er9zsqqsy43fwz8es2wnn65rh0udc05tumdnx5xagvzd88ptncspmesdqhygcrvpf2
-
 @ 3f770d65:7a745b24
2025-04-21 00:15:06
@ 3f770d65:7a745b24
2025-04-21 00:15:06At the recent Launch Music Festival and Conference in Lancaster, PA, featuring over 120 musicians across three days, I volunteered my time with Tunestr and Phantom Power Music's initiative to introduce artists to Bitcoin, Nostr, and the value-for-value model. Tunestr sponsored a stage, live-streaming 21 bands to platforms like Tunestr.io, Fountain.fm and other Nostr/Podcasting 2.0 apps and on-boarding as many others as possible at our conference booth. You may have seen me spamming about this over the last few days.
V4V Earnings
Day 1: 180,000 sats
Day 2: 300,000 sats
Day 3: Over 500,000 sats
Who?
Here are the artists that were on-boarded to Fountain and were live streaming on the Value-for-Value stage:
nostr:npub1cruu4z0hwg7n3r2k7262vx8jsmra3xpku85frl5fnfvrwz7rd7mq7e403w nostr:npub12xeh3n7w8700z4tpd6xlhlvg4vtg4pvpxd584ll5sva539tutc3q0tn3tz nostr:npub1rc80p4v60uzfhvdgxemhvcqnzdj7t59xujxdy0lcjxml3uwdezyqtrpe0j @npub16vxr4pc2ww3yaez9q4s53zkejjfd0djs9lfe55sjhnqkh nostr:npub10uspdzg4fl7md95mqnjszxx82ckdly8ezac0t3s06a0gsf4f3lys8ypeak nostr:npub1gnyzexr40qut0za2c4a0x27p4e3qc22wekhcw3uvdx8mwa3pen0s9z90wk nostr:npub13qrrw2h4z52m7jh0spefrwtysl4psfkfv6j4j672se5hkhvtyw7qu0almy nostr:npub1p0kuqxxw2mxczc90vcurvfq7ljuw2394kkqk6gqnn2cq0y9eq5nq87jtkk nostr:npub182kq0sdp7chm67uq58cf4vvl3lk37z8mm5k5067xe09fqqaaxjsqlcazej nostr:npub162hr8kd96vxlanvggl08hmyy37qsn8ehgj7za7squl83um56epnswkr399 nostr:npub17jzk5ex2rafres09c4dnn5mm00eejye6nrurnlla6yn22zcpl7vqg6vhvx nostr:npub176rnksulheuanfx8y8cr2mrth4lh33svvpztggjjm6j2pqw6m56sq7s9vz nostr:npub1akv7t7xpalhsc4nseljs0c886jzuhq8u42qdcwvu972f3mme9tjsgp5xxk nostr:npub18x0gv872489lrczp9d9m4hx59r754x7p9rg2jkgvt7ul3kuqewtqsssn24
Many more musicians were on-boarded to Fountain, however, we were unable to obtain all of their npubs.
THANK YOU TO ALL ZAPPERS AND BOOSTERS!
Musicians “Get It”
My key takeaway was the musicians' absolute understanding that the current digital landscape along with legacy social media is failing them. Every artist I spoke with recognized how algorithms hinder fan connection and how gatekeepers prevent fair compensation for their work. They all use Spotify, but they only do so out of necessity. They felt the music industry is primed for both a social and monetary revolution. Some of them were even speaking my language…
Because of this, concepts like decentralization, censorship resistance, owning your content, and controlling your social graph weren't just understood by them, they were instantly embraced. The excitement was real; they immediately saw the potential and agreed with me. Bitcoin and Nostr felt genuinely punk rock and that helped a lot of them identify with what we were offering them.
The Tools and the Issues
While the Nostr ecosystem offers a wide variety of tools, we focused on introducing three key applications at this event to keep things clear for newcomers:
- Fountain, with a music focus, was the primary tool for onboarding attendees onto Nostr. Fountain was also chosen thanks to Fountain’s built-in Lightning wallet.
- Primal, as a social alternative, was demonstrated to show how users can take their Nostr identity and content seamlessly between different applications.
- Tunestr.io, lastly was showcased for its live video streaming capabilities.
Although we highlighted these three, we did inform attendees about the broader range of available apps and pointed them to
nostrapps.comif they wanted to explore further, aiming to educate without overwhelming them.This review highlights several UX issues with the Fountain app, particularly concerning profile updates, wallet functionality, and user discovery. While Fountain does work well, these minor hiccups make it extremely hard for on-boarding and education.
- Profile Issues:
- When a user edits their profile (e.g., Username/Nostr address, Lightning address) either during or after creation, the changes don't appear to consistently update across the app or sync correctly with Nostr relays.
- Specifically, the main profile display continues to show the old default Username/Nostr address and Lightning address inside Fountain and on other Nostr clients.
- However, the updated Username/Nostr address does appear on https://fountain.fm (chosen-username@fountain.fm) and is visible within the "Edit Profile" screen itself in the app.
- This inconsistency is confusing for users, as they see their updated information in some places but not on their main public-facing profile within the app. I confirmed this by observing a new user sign up and edit their username – the edit screen showed the new name, but the profile display in Fountain did not update and we did not see it inside Primal, Damus, Amethyst, etc.
- Wallet Limitations:
- The app's built-in wallet cannot scan Lightning address QR codes to initiate payments.
- This caused problems during the event where users imported Bitcoin from Azte.co vouchers into their Fountain wallets. When they tried to Zap a band by scanning a QR code on the live tally board, Fountain displayed an error message stating the invoice or QR code was invalid.
- While suggesting musicians install Primal as a second Nostr app was a potential fix for the QR code issue, (and I mentioned it to some), the burden of onboarding users onto two separate applications, potentially managing two different wallets, and explaining which one works for specific tasks creates a confusing and frustrating user experience.
- Search Difficulties:
- Finding other users within the Fountain app is challenging. I was unable to find profiles from brand new users by entering their chosen Fountain username.
- To find a new user, I had to resort to visiting their profile on the web (fountain.fm/username) to retrieve their npub. Then, open Primal and follow them. Finally, when searching for their username, since I was now following them, I was able to find their profile.
- This search issue is compounded by the profile syncing problem mentioned earlier, as even if found via other clients, their displayed information is outdated.
- Searching for the event to Boost/Zap inside Fountain was harder than it should have been the first two days as the live stream did not appear at the top of the screen inside the tap. This was resolved on the third day of the event.
Improving the Onboarding Experience
To better support user growth, educators and on-boarders need more feature complete and user-friendly applications. I love our developers and I will always sing their praises from the highest mountain tops, however I also recognize that the current tools present challenges that hinder a smooth onboarding experience.
One potential approach explored was guiding users to use Primal (including its built-in wallet) in conjunction with Wavlake via Nostr Wallet Connect (NWC). While this could facilitate certain functions like music streaming, zaps, and QR code scanning (which require both Primal and Wavlake apps), Wavlake itself has usability issues. These include inconsistent or separate profiles between web and mobile apps, persistent "Login" buttons even when logged in on the mobile app with a Nostr identity, and the minor inconvenience of needing two separate applications. Although NWC setup is relatively easy and helps streamline the process, the need to switch between apps adds complexity, especially when time is limited and we’re aiming to showcase the benefits of this new system.
Ultimately, we need applications that are more feature-complete and intuitive for mainstream users to improve the onboarding experience significantly.
Looking forward to the future
I anticipate that most of these issues will be resolved when these applications address them in the near future. Specifically, this would involve Fountain fixing its profile issues and integrating Nostr Wallet Connect (NWC) to allow users to utilize their Primal wallet, or by enabling the scanning of QR codes that pay out to Lightning addresses. Alternatively, if Wavlake resolves the consistency problems mentioned earlier, this would also significantly improve the situation giving us two viable solutions for musicians.
My ideal onboarding event experience would involve having all the previously mentioned issues resolved. Additionally, I would love to see every attendee receive a $5 or $10 voucher to help them start engaging with value-for-value, rather than just the limited number we distributed recently. The goal is to have everyone actively zapping and sending Bitcoin throughout the event. Maybe we can find a large sponsor to facilitate this in the future?
What's particularly exciting is the Launch conference's strong interest in integrating value-for-value across their entire program for all musicians and speakers at their next event in Dallas, Texas, coming later this fall. This presents a significant opportunity to onboard over 100+ musicians to Bitcoin and Nostr, which in turn will help onboard their fans and supporters.
We need significantly more zaps and more zappers! It's unreasonable to expect the same dedicated individuals to continuously support new users; they are being bled dry. A shift is needed towards more people using bitcoin for everyday transactions, treating it as money. This brings me back to my ideal onboarding experience: securing a sponsor to essentially give participants bitcoin funds specifically for zapping and tipping artists. This method serves as a practical lesson in using bitcoin as money and showcases the value-for-value principle from the outset.
-
 @ fbf0e434:e1be6a39
2025-05-22 06:41:25
@ fbf0e434:e1be6a39
2025-05-22 06:41:25Hackathon 概要
JAMHacks 9 于 2025 年 5 月 16 日至 18 日在滑铁卢大学举办。作为 JAMHacks 系列的第九届黑客松,该活动汇聚了 170 名高中黑客爱好者,最终评审通过 49 个项目,充分彰显了年轻开发者的技术实力。此次黑客松旨在为高中生打造培育成长的平台,搭配工作坊与互动活动,助力提升技术能力并拓展社交网络。
参与者带来了丰富的项目成果:基于 Pico-8 的创意开发、运用 MongoDB Atlas 的创新应用,以及展示新兴技术应用的生成式 AI 模型项目。活动设置多个奖项类别,包括最佳新手项目、最佳开发者工具、生成式 AI 最佳应用等。奖品涵盖智能手表、无人机、QuillBot 连帽衫,以及其他黑客松的参赛资格。
除技术成果外,JAMHacks 9 同样注重营造趣味互动体验,特别举办扑克之夜、社交派对等活动。此次黑客松成功为年轻开发者搭建了技能提升、创意孵化与专业联结的平台,切实践行其推动科技行业包容性与可及性的愿景。
Hackathon 获奖者
总奖项获奖者
- Mr. Goose:一个有趣的VS Code扩展,为初学者提供提示和鼓励,促进学习而不直接解决问题。
- Guideline:一个基于AR的工具,通过增强现实引导初学电子爱好者进行面包板组装。
- ARmatica:将2D硬件示意图转换为3D AR模型,通过改进可视化增强工程和原型设计过程。
初学者赛道奖项获奖者
- Duedle:一个任务管理应用,利用AI将大型任务分解为可管理的小任务,并提供进度跟踪以提高生产力。
单人赛道奖项获奖者
- Lofied:一个Python应用程序,将Spotify播放列表变为lo-fi版本,具有音乐分离和乐谱生成功能。
女性赛道奖项获奖者
- Doomlings:结合游戏化和教育任务,通过战斗游戏界面提高学生的学习和参与。
Warp 赛道奖项获奖者
Hack Canada 赛道奖项获奖者
- Dionysus:一个用于组织协作活动和参与的平台,提供实时活动管理的统一界面。
MLH 赛道奖项获奖者
- Karma:一个记录和分享积极行动的社交平台,促进自我提升和环境保护,以鼓励社区参与。
- helpidontknowhowtonetworkin.tech:一个使用面部识别和LinkedIn数据的AI驱动网络助手,帮助在活动中建立专业联系。
- SnapCAD:从图像或图纸生成可定制的3D模型,简化工程项目的集成。
PEX Labs 奖项获奖者
- Arctic Explorer:一个Pico-8开放世界游戏,通过探索北极环境促进可持续实践,可以扩展附加小游戏和地图。
查看所有项目 JAMHacks 9。
关于组织者
JAMHacks
JAMHacks 在科技和区块链领域因促进技术爱好者之间的创新与合作而备受认可。该组织擅长举办Hackathon,为开发现实世界挑战的实际解决方案提供了一个平台。JAMHacks 聚焦于技术赋权,已组织多场活动,吸引了来自不同背景的参与者。他们的倡议强调技术技能发展和网络拓展,充分体现了他们致力于推进技术教育和培养一个包容的社区,为有抱负的技术人员和开发者服务。
-
 @ 90152b7f:04e57401
2025-05-22 02:30:51
@ 90152b7f:04e57401
2025-05-22 02:30:51WikiLeaks The Global Intelligence Files
Released on 2013-03-11 00:00 GMT
| Email-ID | 364528 | | -------- | --------------------------- | | Date | 2007-09-20 03:02:09 | | From | os@stratfor.com | | To | intelligence@stratfor.com |
Rice, Israeli FM discuss Israeli decision of defining Gaza as "hostile\ entity"\ 2007-09-20 00:41:16\ http://news.xinhuanet.com/english/2007-09/20/content_6756959.htm\ \ JERUSALEM, Sept. 19 (Xinhua) -- Visiting U.S. Secretary of State\ Condoleezza Rice met with Israeli Foreign Minister Tzipi Livni on\ Wednesday, the two discussed Israel's decision that defined the Hamas-\ controlled Gaza Strip as a "hostile entity."\ \ At a joint press conference held after their meeting, Rice told the\ reporters that the Palestinian Hamas is a "hostile entity" to U.S. as well.\ \ Israel's Security Cabinet declared the Gaza Strip a "hostile entity" on\ Wednesday ahead of Rice's visit and said it would cutoff power and fuel\ supplies to the strip.\ \ Gaza's population, largely impoverished, is almost entirely\ dependent on Israel for the supply of electricity, water and fuel, and a\ cutoff would deepen their hardship.\ \ Since the Hamas takeover in June, Israel has closed crossings with\ Gaza almost entirely, allowing in only humanitarian aid. However, Rice\ reiterated that the United States will not abandon the innocent\ Palestinians in Gaza.\ \ For her part, Livni said that Israel withdrew from the Gaza Strip\ two years ago, hoping that could lead to the establishment of a\ Palestinian state, but only get almost daily rocket attacks in return.\ \ "We expect the Palestinians to understand that Israeli security is\ in their own interests," Livni said, adding that Palestinians must\ understand "supporting Hamas won't help them."\ \ The Israeli Security Cabinet's declaration of Gaza as an "hostile\ entity" could lead to the most severe retaliatory measure taken by\ Israel against Palestinian rocket fire from the strip.\ \ The crude rocket attacks have killed 12 people in southern Israel in\ the past seven years, injured dozens more and badly disrupted daily life\ in the region.\ \ Last week, a Qassam rocket hit an Israeli military base near the\ Gaza Strip, wounding over 60 soldiers in the attack. The attack then\ sparked calls for the government to take harsh response against the Gaza\ Strip, which has been under the control of Hamas since it violently took\ over the enclave in mid June.\ \ The Jewish states has been holding Hamas responsible for the attack,\ although the movement has not been directly involved in the attacks.\ Israel still accused the Islamic movement of doing little to halt them.\ \ Apart from the Palestinian issue, Rice also discussed with Livni\ issues about Iran, Lebanon and the Middle East peace progress.\ \ She said Israel and the Palestinians are showing good faith in their\ negotiations towards a "two state solution."\ \ Regarding Iranian issues, Rice told reporters that diplomatic mean\ is a part of efforts to halt the Iranian nuclear program, but stressed\ it "has to have teeth."\ \ Rice, who had visited this region in August, is also expected to\ hold separate meetings on Wednesday with Israeli Defense Minister Ehud\ Barak and the Likud party head Binyamin Netanyahu.\ \ She will then hold a dinner meeting with Israeli Prime Minister Ehud\ Olmert.\ \ Rice is scheduled to leave here Thursday afternoon and visit the\ West Bank city of Ramallah for meetings with the Palestinian leadership\ on Thursday.
-
 @ 0176967e:1e6f471e
2024-07-21 11:20:40
@ 0176967e:1e6f471e
2024-07-21 11:20:40Ako sa snažím praktizovať LunarPunk bez budovania opcionality "odchodom" do zahraničia. Nie každý je ochotný alebo schopný meniť "miesto", ako však v takom prípade minimalizovať interakciu so štátom? Nie návod, skôr postrehy z bežného života.
-
 @ 2f29aa33:38ac6f13
2025-05-17 12:59:01
@ 2f29aa33:38ac6f13
2025-05-17 12:59:01The Myth and the Magic
Picture this: a group of investors, huddled around a glowing computer screen, nervously watching Bitcoin’s price. Suddenly, someone produces a stick-no ordinary stick, but a magical one. With a mischievous grin, they poke the Bitcoin. The price leaps upward. Cheers erupt. The legend of the Bitcoin stick is born.
But why does poking Bitcoin with a stick make the price go up? Why does it only work for a lucky few? And what does the data say about this mysterious phenomenon? Let’s dig in, laugh a little, and maybe learn the secret to market-moving magic.

The Statistical Side of Stick-Poking
Bitcoin’s Price: The Wild Ride
Bitcoin’s price is famous for its unpredictability. In the past year, it’s soared, dipped, and soared again, sometimes gaining more than 50% in just a few months. On a good day, billions of dollars flow through Bitcoin trades, and the price can jump thousands in a matter of hours. Clearly, something is making this happen-and it’s not just spreadsheets and financial news.
What Actually Moves the Price?
-
Scarcity: Only 21 million Bitcoins will ever exist. When more people want in, the price jumps.
-
Big News: Announcements, rumors, and meme-worthy moments can send the price flying.
-
FOMO: When people see Bitcoin rising, they rush to buy, pushing it even higher.
-
Liquidations: When traders betting against Bitcoin get squeezed, it triggers a chain reaction of buying.
But let’s be honest: none of this is as fun as poking Bitcoin with a stick.

The Magical Stick: Not Your Average Twig
Why Not Every Stick Works
You can’t just grab any old branch and expect Bitcoin to dance. The magical stick is a rare artifact, forged in the fires of internet memes and blessed by the spirit of Satoshi. Only a chosen few possess it-and when they poke, the market listens.
Signs You Have the Magical Stick
-
When you poke, Bitcoin’s price immediately jumps a few percent.
-
Your stick glows with meme energy and possibly sparkles with digital dust.
-
You have a knack for timing your poke right after a big event, like a halving or a celebrity tweet.
-
Your stick is rumored to have been whittled from the original blockchain itself.
Why Most Sticks Fail
-
No Meme Power: If your stick isn’t funny, Bitcoin ignores you.
-
Bad Timing: Poking during a bear market just annoys the blockchain.
-
Not Enough Hype: If the bitcoin community isn’t watching, your poke is just a poke.
-
Lack of Magic: Some sticks are just sticks. Sad, but true.

The Data: When the Stick Strikes
Let’s look at some numbers:
-
In the last month, Bitcoin’s price jumped over 20% right after a flurry of memes and stick-poking jokes.
-
Over the past year, every major price surge was accompanied by a wave of internet hype, stick memes, or wild speculation.
-
In the past five years, Bitcoin’s biggest leaps always seemed to follow some kind of magical event-whether a halving, a viral tweet, or a mysterious poke.
Coincidence? Maybe. But the pattern is clear: the stick works-at least when it’s magical.

The Role of Memes, Magic, and Mayhem
Bitcoin’s price is like a cat: unpredictable, easily startled, and sometimes it just wants to be left alone. But when the right meme pops up, or the right stick pokes at just the right time, the price can leap in ways that defy logic.
The bitcoin community knows this. That’s why, when Bitcoin’s stuck in a rut, you’ll see a flood of stick memes, GIFs, and magical thinking. Sometimes, it actually works.

The Secret’s in the Stick (and the Laughs)
So, does poking Bitcoin with a stick really make the price go up? If your stick is magical-blessed by memes, timed perfectly, and watched by millions-absolutely. The statistics show that hype, humor, and a little bit of luck can move markets as much as any financial report.
Next time you see Bitcoin stalling, don’t just sit there. Grab your stick, channel your inner meme wizard, and give it a poke. Who knows? You might just be the next legend in the world of bitcoin magic.
And if your stick doesn’t work, don’t worry. Sometimes, the real magic is in the laughter along the way.

-aco
@block height: 897,104
-
-
 @ 04c915da:3dfbecc9
2025-05-16 18:06:46
@ 04c915da:3dfbecc9
2025-05-16 18:06:46Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Using stolen bitcoin for the reserve creates a perverse incentive. If governments see bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 58537364:705b4b85
2025-05-22 05:42:27
@ 58537364:705b4b85
2025-05-22 05:42:27คนเรามักจะเห็นคุณค่าของสิ่งใด ส่วนใหญ่ก็ใน ๒ สถานการณ์คือ หนึ่ง ตอนที่ยังไม่ได้มา หรือ สอง ตอนที่เสียไปแล้ว
อันนี้มันเป็นโศกนาฏกรรม ที่เกิดขึ้นกับผู้คนจำนวนมาก การที่คนเรามีสิ่งดีๆ แต่ว่าเราไม่เห็นคุณค่า เพราะว่าเรามองออกไปนอกตัว ไปเห็นแต่สิ่งที่ตัวเองไม่มี อยากจะได้มา
คล้ายๆ กับเรื่อง หมาคาบเนื้อในนิทานอีสป ตอนเด็กๆ เราคงจำได้ มีหมาตัวหนึ่งคาบเนื้อมา เนื้อชิ้นใหญ่เลย มันดีใจมากแล้วมันก็วิ่งไปยังที่ที่ มันจะได้กินเนื้ออย่างมีความสุข มีช่วงหนึ่งก็ต้องเดินข้ามสะพาน มันก็ชะโงกหน้าไปมองที่ลำธารหรือลำคลอง
ก็เห็นเงาตัวเอง เงานั่นมันก็ใหญ่ แล้วมันก็พบว่าในเงานั้น เนื้อในเงามันใหญ่กว่าเนื้อที่ตัวเองคาบ มันอยากได้เนื้อก้อนนั้นมากเลย เพราะว่ามันเป็นก้อนที่ใหญ่กว่า
มันก็เลยอ้าปาก เพื่อที่จะไปงับเนื้อในเงานั้น พอมันอ้าปาก ก็ปรากฏว่าเนื้อในปาก ก็หลุดตกลงแม่น้ำ แล้วเนื้อในเงานั้นก็หายไป เป็นอันว่าหมดเลย อดทั้ง 2 อย่าง .
ฉะนั้น คนเราถ้าหากเรา กลับมาเห็นคุณค่าของสิ่งที่เรามีอยู่ เราจะมีความสุขได้ง่าย อาจจะไม่ใช่สิ่งของ อาจจะไม่ใช่ผู้คน แต่อาจจะเป็นสุขภาพของเรา
อาจจะได้แก่ ลมหายใจของเรา ที่ยังหายใจได้ปกติ รวมถึงการที่ เรายังเดินเหินไปไหนมาไหนได้ การที่เรายังมองเห็น การที่เรายังได้ยิน
หลายคนมีสิ่งนี้อยู่ในตัว แต่กลับไม่เห็นค่า และไม่รู้สึกว่าตัวเองโชคดี กลับไปมองว่า ฉันยังไม่มีโน่นยังไม่มีนี่ ไม่มีบ้าน ไม่มีรถ ไม่มีเงิน
รู้สึกว่าทุกข์ระทมเหลือเกิน
ทำไมฉันจึงลำบากแบบนี้ ทั้งที่ตัวเองก็มีสิ่งดีๆ ในตัว สุขภาพ ความปกติสุข อิสรภาพที่เดินไปไหนมาไหนได้
แต่กลับไม่เห็นค่า เพราะว่ามัวแต่ไปสนใจสิ่งที่ตัวเองยังไม่มี
ซึ่งเป็นอนาคต
ถ้าเราหันกลับมาเห็นคุณค่าของสิ่งที่เรามีอยู่ แล้วก็ไม่ไปพะวงหรือให้ความสนใจกับสิ่งที่ยังไม่มี เราจะมีความสุขได้ง่าย อันนี้คือ ความหมายหนึ่งของการทำปัจจุบันให้ดีที่สุด
…
การทำปัจจุบันให้ดีที่สุด พระอาจารย์ไพศาล วิสาโล

-
 @ cd17b2d6:8cc53332
2025-05-21 22:28:09
@ cd17b2d6:8cc53332
2025-05-21 22:28:09Looking to simulate a USDT deposit that appears instantly in a wallet — with no blockchain confirmation, no real spend, and no trace?
You’re in the right place.
🔗 Buy Flash USDT Now This product sends Flash USDT directly to your TRC20, ERC20, or BEP20 wallet address — appears like a real deposit, but disappears after a set time or block depth.
✅ Perfect for: Simulating token inflows Wallet stress testing “Proof of funds” display Flash USDT is ideal for developers, trainers, UI testers, and blockchain researchers — and it’s fully customizable.
🧠 What Is Flash USDT? Flash USDT is a synthetic transaction that mimics a real Tether transfer. It shows up instantly in a wallet balance, and it’s confirmed on-chain — and expires after a set duration.
This makes it:
Visible on wallet interfaces Time-limited (auto-disappears cleanly) Undetectable on block explorers after expiry It’s the smartest, safest way to simulate high-value transactions without real crypto.
🛠️ Flash USDT Software – Your Own USDT Flasher at Your Fingertips Want to control the flash? Run your own operations? Flash unlimited wallets?
🔗 Buy Flash USDT Software
This is your all-in-one USDT flasher tool, built for TRC20, ERC20, and BEP20 chains. It gives you full control to:
Send custom USDT amounts Set custom expiry time (e.g., 30–360 days) Flash multiple wallets Choose between networks (Tron, ETH, BSC) You can simulate any amount, to any supported wallet, from your own system.
No third-party access. No blockchain fee. No trace left behind.
💥 Why Our Flash USDT & Software Stands Out Feature Flash USDT Flash USDT Software One-time flash send ✅ Yes Optional Full sender control ❌ No ✅ Yes TRC20 / ERC20 / BEP20 ✅ Yes ✅ Yes Custom duration/expiry Limited ✅ Yes Unlimited usage ❌ One-off ✅ Yes Whether you’re flashing for wallet testing, demoing investor dashboards, or simulating balance flows, our tools deliver realism without risk.
🛒 Ready to Buy Flash USDT or the Software? Skip the wait. Skip the scammers. You’re one click away from real control.
👉 Buy Flash USDT 👉 Buy Flash USDT Software
📞 Support or live walkthrough?
💬 Telegram: @cryptoflashingtool 📱 WhatsApp: +1 770-666-2531
🚫 Legal Notice These tools are intended for:
Educational purposes Demo environments Wallet and UI testing They are not for illegal use or financial deception. Any misuse is your full responsibility.
Final Call: Need to flash USDT? Want full control? Don’t wait for another “maybe” tool.
Get your Flash USDT or Flashing Software today and simulate like a pro.
🔗 Buy Now → Flash USDT 🔗 Buy Now → Flash USDT Software 💬 Telegram: @cryptoflashingtool 📱 WhatsApp: +1 770-666-2531Looking to simulate a USDT deposit that appears instantly in a wallet — with no blockchain confirmation, no real spend, and no trace?
You’re in the right place.
Buy Flash USDT Now\ This product sends Flash USDT directly to your TRC20, ERC20, or BEP20 wallet address — appears like a real deposit, but disappears after a set time or block depth.
Perfect for:
- Simulating token inflows
- Wallet stress testing
- “Proof of funds” display
Flash USDT is ideal for developers, trainers, UI testers, and blockchain researchers — and it’s fully customizable.
What Is Flash USDT?
Flash USDT is a synthetic transaction that mimics a real Tether transfer. It shows up instantly in a wallet balance, and it’s confirmed on-chain — and expires after a set duration.
This makes it:
- Visible on wallet interfaces
- Time-limited (auto-disappears cleanly)
- Undetectable on block explorers after expiry
It’s the smartest, safest way to simulate high-value transactions without real crypto.
Flash USDT Software – Your Own USDT Flasher at Your Fingertips
Want to control the flash?\ Run your own operations?\ Flash unlimited wallets?
This is your all-in-one USDT flasher tool, built for TRC20, ERC20, and BEP20 chains. It gives you full control to:
- Send custom USDT amounts
- Set custom expiry time (e.g., 30–360 days)
- Flash multiple wallets
- Choose between networks (Tron, ETH, BSC)
You can simulate any amount, to any supported wallet, from your own system.
No third-party access.\ No blockchain fee.\ No trace left behind.
Why Our Flash USDT & Software Stands Out
Feature
Flash USDT
Flash USDT Software
One-time flash send
Yes
Optional
Full sender control
No
Yes
TRC20 / ERC20 / BEP20
Yes
Yes
Custom duration/expiry
Limited
Yes
Unlimited usage
One-off
Yes
Whether you’re flashing for wallet testing, demoing investor dashboards, or simulating balance flows, our tools deliver realism without risk.
Ready to Buy Flash USDT or the Software?
Skip the wait. Skip the scammers.\ You’re one click away from real control.
Support or live walkthrough?
Telegram: @cryptoflashingtool
WhatsApp: +1 770-666-2531
Legal Notice
These tools are intended for:
- Educational purposes
- Demo environments
- Wallet and UI testing
They are not for illegal use or financial deception. Any misuse is your full responsibility.
Final Call:
Need to flash USDT? Want full control?\ Don’t wait for another “maybe” tool.
Get your Flash USDT or Flashing Software today and simulate like a pro.
Telegram: @cryptoflashingtool
WhatsApp: +1 770-666-2531
-
 @ 592295cf:413a0db9
2025-04-13 15:52:02
@ 592295cf:413a0db9
2025-04-13 15:52:02Nostur is capable of login with bunker
Photo, note by Fabian
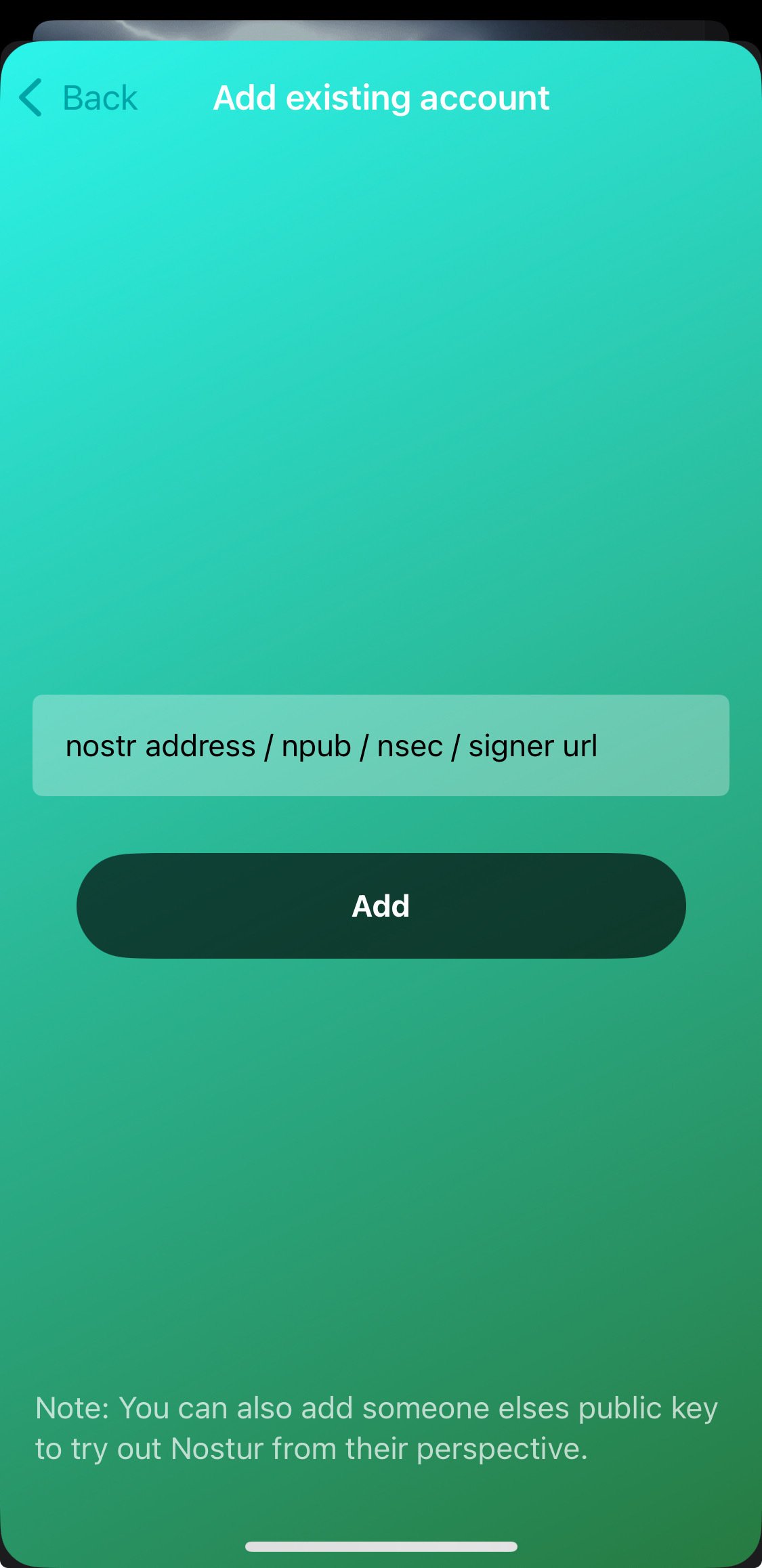
nostr:nevent1qvzqqqqqqypzqkfzjh8jkzd8l9247sadku6vhm52snhgjtknlyeku6sfkeqn5rdeqyf8wumn8ghj7mn0wd68ytnvw5hxkef0qyg8wumn8ghj7mn0wd68ytnddakj7qpqxfktwlm2qdkpxy556e4yg4l8p6v8930nfyzg7p3vsknk7krutz0s8znjtq
When you decide to share an app you have to know a lot about that app. For example the nstart feature that you can share your friends, has a "smart pack" and the app can onboard, at least following the link --> Apps-integration
So let's try to read and bring a bit to the summary of the thing. Only the one about the profiles, which you don't know exactly how it will end, you have to try it before sending to someone. the second point is that it says that there is no "support encryption, so it cannot be used for DMs apps".
there was an update of nstart, now it shows you
the names of the bunkers, maybe now it's too much, decide if it does 3/2 4/2 or just automatic.
So they talked about frost in the hodlbod podcast. I didn't understand much except that they said to test frost and report the feedback. Tomorrow I'll try to download igloo and frost+nos2ex
So I have to wait for let's say version 0_1_0 of igloo now it is (0_0_4) and
maybe there will be the version of the extension ready.
Sebastix also found it difficult but I think he was trying to install the server, which didn't even occur to me. Anyway I leave you the note if you want to go deeper...
nostr:nevent1qvzqqqqqqypzqpnrnguxe8qszsshvgkvhn6qjzxy7xsvx03rlrtddr62haj4lrm3qytkummnw3ez66tyvgaz7tmrv93ksefdwfjkccteqqs2wzkkx220e24revkpxmdzkqj73rnz0reeenjwgy53g36hlkdgurgrs5e62
Let's see if I can download the video. ok Downloaded. Video .mov
If you don't want to watch I'll leave a little description
1 Download and install igloo, from the frost page. 2 Create a new key set, you can generate or copy an existing key. 3. Choose the options for the key and now they become multiple keys 4. Created a group of credentials. 5. Save the two credentials with a password and bring the third into the browser extension that it creates from the repository, it says that there will be a bootable extension for chrome. 6. Copy the third key and the group package key into the application node. 7. Once you have entered these keys you can finish the operation (and you have backed up the other two) in igloo. 8. When it goes forward it finds itself with two keys, both encrypted with passwords. 9. Since it is a three of two, it just needs to activate a key in igloo and it starts communicating "startsigner". 10. Opens a nostr client and connects with frost2sx and writes a note 11. Shows the log, and says that if you enter two keys it can generate a third, invalidating the old one (I assume)
-
 @ 04c915da:3dfbecc9
2025-05-16 17:59:23
@ 04c915da:3dfbecc9
2025-05-16 17:59:23Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ c1e6505c:02b3157e
2025-05-22 03:44:39
@ c1e6505c:02b3157e
2025-05-22 03:44:39This is day two of testing the Leica Summaron 35mm f2.8 on the Fujifilm X-Pro2.
The first part of this story you can find here on StackerNews**
TL;DR: I think I’m really enjoying this lens.
I went into it thinking I’d probably just sell it since it was gifted to me - assumed I wouldn’t like it. But after just a couple of days with it mounted on the X-Pro2, I’ve been surprisingly drawn to it.
Shooting wide open at f2.8 (which is how I’m testing it - to best reveal the lens’s character), the soft roll-off is really pleasing. It feels organic. The lens is over 50 years old, so I expected some quirks-but the quality feels natural, not overly “vintage". Takes the digital edge off.
The short focus throw is also really nice. Compared to the Summicron 35mm f2 v3 I usually shoot on my M262 (which has a longer throw), the Summaron feels tighter and more responsive when zone focusing.
One gripe: the infinity lock. It’s kind of annoying. I find myself accidentally locking it too often, but I’m getting used to holding the button down as I rotate the ring. I’ve read others complain about it, so I know I’m not alone there.
Most of these shots were from a bike ride to the river - about 6 miles out to swim and enjoy the sun. Perfect day for making a few photos.
This kind of work is honestly just fun. I enjoy the process, and even more so once I’m happy with the results and can share them.
Still building confidence in my work over time. I think I’m slowly refining my style - even if the subject matter is simple. Easier said than done, as any editor/curator knows (and I say this as one through NOICE Magazine).
Let me know what you think. I’ll try to upload higher resolution versions this time around (but not too high).
*Also, I use a program called Dehancer for creating the grain in these photographs. I highly recommend the program actually, I've been using it for a long time. If you would like to try it out, I have a promo code. Use "Pictureroom" for 10% off I believe.
You can further support me and my work by sending sats to colincz\@getalby.com. Thank you.
(note* this is being publised from the updated Primal reads client)
-
 @ 0176967e:1e6f471e
2024-07-20 08:28:00
@ 0176967e:1e6f471e
2024-07-20 08:28:00Tento rok vás čaká workshop na tému "oranžové leto" s Jurajom Bednárom a Mariannou Sádeckou. Dozviete sa ako mení naše vnímanie skúsenosť s Bitcoinom, ako sa navigovať v dnešnom svete a odstrániť mentálnu hmlu spôsobenú fiat životom.
Na workshop je potrebný extra lístok (môžete si ho dokúpiť aj na mieste).
Pre viac informácií o oranžovom lete odporúčame pred workshopom vypočuťi si podcast na túto tému.
-
 @ 592295cf:413a0db9
2025-04-05 07:26:23
@ 592295cf:413a0db9
2025-04-05 07:26:23[Edit] I tried to get the slides and an audio file, from Constant's talk at NostRiga, about 8 months ago
1.
Nostr's adoption thesis
The less you define, the more you imply
by Wouter Constant
2.
Dutch Bitcoiner
AntiHashedPodcast
Writing Book about nostr
00:40
3.
What this presentation about
A protocols design includes initself a thesis
on protocol adoption, due to underlying assumptions
1:17
4.
Examples
Governments/Academic: Pubhubs (Matrix)
Bussiness: Bluesky
Foss: Nostr
1:58
5.
What constitutes minimal viability?
Pubhubs (Matrix): make is "safe" for user
Bluesky: liability and monetization
Foss: Simpel for developer
4:03
6.
The Point of Nostr
Capture network effects through interoperability
4:43
7.
Three assumptions
The direction is workable
Method is workable
Motivation and means are sufficient
5:27
8.
Assumption 1
The asymmetric cryptography paradigm is a good idea
6:16
9.
Nostr is a exponent of the key-pair paradigm.
And Basicly just that.
6.52
10.
Keys suck
Protect a secret that you are supposed use all the time.
7:37
11.
Assumption two
The unaddressed things will be figured out within a 'meta-design consensus'
8:11
12.
Nostr's base protocol is not minimally viable for anything, except own development.
8:25
13.
Complexity leads to capture;
i.e. free and open in the name,
controlled in pratice
9:54
14.
Meta-design consensus
Buildings things 'note centric' mantains interoperability.
11:51
15.
Assumption three
the nightmare is scary;
the cream is appealing.
12:41
16.
Get it minimally viable,
for whatever target,
such that it is not a waste of time.
13:23
17.
Summarize
We are in a nightmare.
Assume key/signature are the way out.
Assume we can Maintain an open stardand while manifesting the dream.
Assume we are motivated enought to bootstrap this to adulthood.
14:01
18.
We want this,
we can do this,
because we have to.
14:12
Thank you for contribuiting
[Edit] Note for audio presentation
nostr:nevent1qvzqqqqqqypzqkfzjh8jkzd8l9247sadku6vhm52snhgjtknlyeku6sfkeqn5rdeqyf8wumn8ghj7mn0wd68ytnvw5hxkef0qyg8wumn8ghj7mn0wd68ytnddakj7qpqqqq6fdnhvp95gqf4k3vxmljh87uvjezpepyt222jl2267q857uwqz7gcke
-
 @ 5ffb8e1b:255b6735
2025-03-29 13:57:02
@ 5ffb8e1b:255b6735
2025-03-29 13:57:02As a fellow Nostrich you might have noticed some of my #arlist posts. It is my effort to curate artists that are active on Nostr and make it easier for other users to find content that they are interested in.
By now I have posted six or seven posts mentioning close to fifty artists, the problem so far is that it's only a list of handles and it is up to reader to click on each in order to find out what are the artist behind the names all about. Now I am going to start creating blog posts with a few artists mentioned in each, with short descriptions of their work and an image or to.
I would love to have some more automated mode of curation but I still couldn't figure out what is a good way for it. I've looked at Listr, Primal custom feeds and Yakihonne curations but none seem to enable me to make a list of npubs that is then turned into a feed that I could publicly share for others to views. Any advice on how to achieve this is VERY welcome !
And now lets get to the first batch of artists I want to share with you.
Eugene Gorbachenko
nostr:npub1082uhnrnxu7v0gesfl78uzj3r89a8ds2gj3dvuvjnw5qlz4a7udqwrqdnd Artist from Ukrain creating amazing realistic watercolor paintings. He is very active on Nostr but is very unnoticed for some stange reason. Make sure to repost the painting that you liked the most to help other Nostr users to discover his great art.
Siritravelsketch
nostr:npub14lqzjhfvdc9psgxzznq8xys8pfq8p4fqsvtr6llyzraq90u9m8fqevhssu a a lovely lady from Thailand making architecture from all around the world spring alive in her ink skethes. Dynamic lines gives it a dreamy magical feel, sometimes supported by soft watercolor strokes takes you to a ferytale layer of reality.
BureuGewas
nostr:npub1k78qzy2s9ap4klshnu9tcmmcnr3msvvaeza94epsgptr7jce6p9sa2ggp4 a a master of the clasic oil painting. From traditional still life to modern day subjects his paintings makes you feel the textures and light of the scene more intense then reality itself.
You can see that I'm no art critic, but I am trying my best. If anyone else is interested to join me in this curration adventure feel free to reach out !
With love, Agi Choote
-
 @ 592295cf:413a0db9
2025-03-29 10:59:52
@ 592295cf:413a0db9
2025-03-29 10:59:52The journey starts from the links in this article nostr-quick-start-guide
Starting from these links building a simple path should not cover everything, because impossible.
Today I saw that Verbiricha in his workshop on his channel used nstart, but then I distracted And I didn't see how he did it.
Go to nstart.me and read: Each user is identified by a cryptographic keypair Public key, Private key (is a lot of stuff)
You can insert a nickname and go, the nickname is not unique
there is a email backup things interesting, but a little boring, i try to generate an email
doesn't even require a strong password ok.
I received the email, great, it shows me the nsec encrypted in clear,
Send a copy of the file with a password, which contains the password encrypted key I know and I know it's a tongue dump.
Multi signer bunker
That's stuff, let's see what he says.
They live the private key and send it to servers and you can recompose it to login at a site of the protocol nostr. If one of these servers goes offline you have the private key that you downloaded first and then reactivate a bunker. All very complicated. But if one of the servers goes offline, how can I remake the split? Maybe he's still testing.
Nobody tells you where these bunkers are.
Okay I have a string that is my bunker (buker://), I downloaded it, easy no, now will tell me which client accepts the bunker.. .
Follow someone before you start?
Is a cluster of 5 people Snowden, Micheal Dilger, jb55, Fiatjaf, Dianele.
I choice Snowden profile, or you can select multiple profiles, extra wild.
Now select 5 clients
Coracle, Chachi, Olas, Nostur, Jumble
The first is Coracle
Login, ok I try to post a note and signing your note the spin does not end.
Maybe the bunker is diffective.
Let's try Chachi
Simpler than Coracle, it has a type login that says bunker. see if I can post
It worked, cool, I managed to post in a group.
Olas is an app but also a website, but on the website requires an extension, which I do not have with this account.
If I download an app how do I pass the bunker on the phone, is it still a password, a qrcode, a qrcode + password, something like that, but many start from the phone so maybe it's easy for them. I try to download it and see if it allows me to connect with a bunker.
Okay I used private-qrcode and it worked, I couldn't do it directly from Olas because it didn't have permissions and the qrcode was < encrypted, so I went to the same site and had the bunker copied and glued on Olas
Ok then I saw that there was the qrcode image of the bunker for apps lol moment
Ok, I liked it, I can say it's a victory.
Looks like none of Snowden's followers are Olas's lover, maybe the smart pack has to predict a photographer or something like that.
Okay I managed to post on Olas, so it works, Expiration time is broken.
As for Nostur, I don't have an ios device so I'm going to another one.
Login with Jumble, it works is a web app
I took almost an hour to do the whole route.
But this was just one link there are two more
Extensions nostr NIP-07
The true path is nip-07-browser-extensions | nostr.net
There are 19 links, maybe there are too many?
I mention the most famous, or active at the moment
- Aka-profiles: Aka-profiles
Alby I don't know if it's a route to recommend
-
Blockcore Blockcore wallet
-
Nos2x Nos2x
-
Nos2xfox (fork for firefox) Nos2xfox
Nostore is (archived, read-only)
Another half hour to search all sites
Nostrapps
Here you can make paths
Then nstart selects Coracle, Chachi, Olas,Nostur and Jumble
Good apps might be Amethyst, 0xchat, Yakihonne, Primal, Damus
for IOS maybe: Primal, Olas, Damus, Nostur, Nos-Social, Nostrmo
On the site there are some categories, I select some with the respective apps
Let's see the categories
Go to Nostrapps and read:
Microbbloging: Primal
Streaming: Zap stream
Blogging: Yakihonne
Group chat: Chachi
Community: Flotilla
Tools: Form *
Discovery: Zapstore (even if it is not in this catrgory)
Direct Message: 0xchat
-
 @ 04c915da:3dfbecc9
2025-05-16 17:12:05
@ 04c915da:3dfbecc9
2025-05-16 17:12:05One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 2dd9250b:6e928072
2025-03-22 00:22:40
@ 2dd9250b:6e928072
2025-03-22 00:22:40Vi recentemente um post onde a pessoa diz que aquele final do filme O Doutrinador (2019) não faz sentido porque mesmo o protagonista explodindo o Palácio dos Três Poderes, não acaba com a corrupção no Brasil.
Progressistas não sabem ler e não conseguem interpretar textos corretamente. O final de Doutrinador não tem a ver com isso, tem a ver com a relação entre o Herói e a sua Cidade.
Nas histórias em quadrinhos há uma ligação entre a cidade e o Super-Herói. Gotham City por exemplo, cria o Batman. Isso é mostrado em The Batman (2022) e em Batman: Cavaleiro das Trevas, quando aquele garoto no final, diz para o Batman não fugir, porque ele queria ver o Batman de novo. E o Comissário Gordon diz que o "Batman é o que a cidade de Gotham precisa."
Batman: Cavaleiro das Trevas Ressurge mostra a cidade de Gotham sendo tomada pela corrupção e pela ideologia do Bane. A Cidade vai definhando em imoralidade e o Bruce, ao olhar da prisão a cidade sendo destruída, decide que o Batman precisa voltar porque se Gotham for destruída, o Batman é destruído junto. E isso o da forças para consegue fugir daquele poço e voltar para salvar Gotham.
Isso também é mostrado em Demolidor. Na série Demolidor o Matt Murdock sempre fala que precisa defender a cidade Cozinha do Inferno; que o Fisk não vai dominar a cidade e fazer o que ele quiser nela. Inclusive na terceira temporada isso fica mais evidente na luta final na mansão do Fisk, onde Matt grita que agora a cidade toda vai saber o que ele fez; a cidade vai ver o mal que ele é para Hell's Kitchen, porque a gente sabe que o Fisk fez de tudo para a imagem do Demolidor entrar e descrédito perante os cidadãos, então o que acontece no final do filme O Doutrinador não significa que ele está acabando com a corrupção quando explode o Congresso, ele está praticamente interrompendo o ciclo do sistema, colocando uma falha em sua engrenagem.
Quando você ouve falar de Brasília, você pensa na corrupção dos políticos, onde a farra acontece,, onde corruptos desviam dinheiro arrecadado dos impostos, impostos estes que são centralizados na União. Então quando você ouve falarem de Brasília, sempre pensa que o pessoal que mora lá, mora junto com tudo de podre que acontece no Brasil.
Logo quando o Doutrinador explode tudo ali, ele está basicamente destruindo o mecanismo que suja Brasília. Ele está fazendo isso naquela cidade. Porque o símbolo da cidade é justamente esse, a farsa de que naquele lugar o povo será ouvido e a justiça será feita. Ele está destruindo a ideologia de que o Estado nos protege, nos dá segurança, saúde e educação. Porque na verdade o Estado só existe para privilegiar os políticos, funcionários públicos de auto escalão, suas famílias e amigos. Enquanto que o povo sofre para sustentar a elite política. O protagonista Miguel entendeu isso quando a filha dele morreu na fila do SUS.


