-
 @ 9c9d2765:16f8c2c2
2025-05-15 05:01:00
@ 9c9d2765:16f8c2c2
2025-05-15 05:01:00CHAPTER NINETEEN
“Please! I’m your sister! I just needed a little help!” she cried dramatically. “How could you do this to your own blood?!”
Gasps echoed through the grand hall.
Guests froze in place, their judgmental stares directed at James. Cameraman didn’t hesitate to raise their lenses. Phones were pulled out. A social media storm was already brewing in real time.
James stood still, eyes narrowed. He didn’t move, didn’t speak.
Tracy, standing beside Helen, discreetly snapped more photos, already typing up the next round of false headlines to feed into the media engine.
Helen smirked at the chaos and whispered, “This is it. The downfall begins.”
But James wasn’t shaken.
With quiet authority, he raised his hand, and two personal bodyguards appeared from the sidelines. He looked Evelyn square in the eye, then said, loud enough for the nearest guests to hear, “Escort this woman outside. She is not my sister. And she has no place here.”
Evelyn’s cries turned more dramatic, but it was clear to the more discerning eyes in the room that something about her act was off. Her appearance was too deliberate, her performance too exaggerated.
As security led her away, some guests began to murmur with skepticism.
“Wait… that woman doesn’t even resemble him.” “Isn’t it strange she showed up right after that story went viral?” “Could this be a setup?”
Suddenly, a hush fell over the grand hall. The doors swung open and in walked Mr. and Mrs. JP, their presence commanding immediate respect and admiration. The atmosphere shifted, charged with reverence. The orchestra paused, and every individual in the room instinctively rose to their feet.
The couple moved with elegance and dignity, their attire speaking volumes of their legacy Mr. JP in a classic black suit with golden cufflinks, and Mrs. JP in an emerald silk gown that shimmered under the chandeliers.
As they made their way toward the stage, hosts and VIPs bowed subtly, showing deference. Whispers rippled through the audience.
"That’s the founder himself..." "And she’s the matriarch elegance personified." "Do you think they know about the scandal?"
When the couple finally ascended the stage, Mr. JP gestured politely for the crowd to take their seats. The applause lingered like a standing ovation for royalty.
Taking the microphone with a measured breath, Mr. JP began, his voice calm, dignified, and layered with authority.
“Distinguished guests,” he said, scanning the crowd with a nod. “Tonight marks a milestone not just in our company’s journey, but in our personal lives. Sixteen years ago, this empire was only a dream... Today, it is a reality that spans borders and inspires millions.”
The audience clapped again, some even rising briefly in acknowledgment.
“We did not build this alone,” he continued, eyes softening. “From those who’ve been with us from the beginning, to the new minds who’ve steered us through recent storms this success belongs to all of you.”
Then, a slight pause.
Mr. JP took a breath, his tone shifting to something deeper.
“Among those responsible for the rebirth of JP Enterprises… is someone very close to me. Someone many of you may not recognize today, but who has been pivotal in our turnaround.”
People exchanged curious glances.
Helen furrowed her brows. Mark leaned forward, visibly tense. Even Tracy, who had been busy on her phone, paused, sensing something big.
Mr. JP looked toward James in the crowd. “Please rise.”
James stood up slowly, every eye in the room locking on him.
Gasps echoed across the hall.
“That’s him?” “The guy from the news?” “The so-called cruel brother?”
Mr. JP smiled proudly.
“Ladies and gentlemen,” he said, his voice growing firm, “the man you see before you is not only the current President of JP Enterprises… but he is also my son James JP.”
Silence fell like a heavy curtain.
Helen's wine glass slipped slightly in her grip. Mark's jaw dropped. Tracy froze.
Mr. JP continued, “Some of you may have seen recent headlines. Falsehoods spread by those who fear his rise. But let me be clear this man was once wrongly accused, cast aside, and even disowned. A mistake I will regret all my life. Yet despite all that, he rebuilt everything. He turned loss into legacy.”
He turned to James, emotion glistening in his eyes. “Son, I’m proud of you. You are not just a worthy heir, you are a better man than I ever was.”
A standing ovation erupted.
The audience rose again, this time with sincere admiration. Applause thundered across the hall.
James slowly approached the stage, his head held high, the moment heavy with vindication. He took the microphone, looked across the sea of faces, some still stunned, some clapping with tears in their eyes.
“Thank you,” he began, his voice steady. “There was a time I stood outside this very building, invisible, broken, and ignored. Today, I stand here not for revenge… but to remind us all: never underestimate the strength of the overlooked.”
The applause grew louder.
“I will protect this company with everything I have,” he declared. “But let it also be known betrayal has no place in this legacy. Truth always finds a way to rise.”
Helen swallowed hard.
Mark clenched his fists beneath the table.
Tracy shrank slightly into her seat.
The atmosphere in the grand ballroom of the JP Enterprises Headquarters was thick with suspense. Mr. JP stood tall behind the polished podium, his presence commanding silence. The air practically crackled with curiosity as the crowd leaned forward in their seats, eager to hear the revelation everyone had been waiting for.
“I know many of you are wondering who my son is,” Mr. JP said, his voice deep and firm, echoing through the hall. “The one who will inherit not just my fortune, but my legacy. The heir to JP Enterprises and everything I have worked for in my lifetime.”
-
 @ 21335073:a244b1ad
2025-05-09 13:56:57
@ 21335073:a244b1ad
2025-05-09 13:56:57Someone asked for my thoughts, so I’ll share them thoughtfully. I’m not here to dictate how to promote Nostr—I’m still learning about it myself. While I’m not new to Nostr, freedom tech is a newer space for me. I’m skilled at advocating for topics I deeply understand, but freedom tech isn’t my expertise, so take my words with a grain of salt. Nothing I say is set in stone.
Those who need Nostr the most are the ones most vulnerable to censorship on other platforms right now. Reaching them requires real-time awareness of global issues and the dynamic relationships between governments and tech providers, which can shift suddenly. Effective Nostr promoters must grasp this and adapt quickly.
The best messengers are people from or closely tied to these at-risk regions—those who truly understand the local political and cultural dynamics. They can connect with those in need when tensions rise. Ideal promoters are rational, trustworthy, passionate about Nostr, but above all, dedicated to amplifying people’s voices when it matters most.
Forget influencers, corporate-backed figures, or traditional online PR—it comes off as inauthentic, corny, desperate and forced. Nostr’s promotion should be grassroots and organic, driven by a few passionate individuals who believe in Nostr and the communities they serve.
The idea that “people won’t join Nostr due to lack of reach” is nonsense. Everyone knows X’s “reach” is mostly with bots. If humans want real conversations, Nostr is the place. X is great for propaganda, but Nostr is for the authentic voices of the people.
Those spreading Nostr must be so passionate they’re willing to onboard others, which is time-consuming but rewarding for the right person. They’ll need to make Nostr and onboarding a core part of who they are. I see no issue with that level of dedication. I’ve been known to get that way myself at times. It’s fun for some folks.
With love, I suggest not adding Bitcoin promotion with Nostr outreach. Zaps already integrate that element naturally. (Still promote within the Bitcoin ecosystem, but this is about reaching vulnerable voices who needed Nostr yesterday.)
To promote Nostr, forget conventional strategies. “Influencers” aren’t the answer. “Influencers” are not the future. A trusted local community member has real influence—reach them. Connect with people seeking Nostr’s benefits but lacking the technical language to express it. This means some in the Nostr community might need to step outside of the Bitcoin bubble, which is uncomfortable but necessary. Thank you in advance to those who are willing to do that.
I don’t know who is paid to promote Nostr, if anyone. This piece isn’t shade. But it’s exhausting to see innocent voices globally silenced on corporate platforms like X while Nostr exists. Last night, I wondered: how many more voices must be censored before the Nostr community gets uncomfortable and thinks creatively to reach the vulnerable?
A warning: the global need for censorship-resistant social media is undeniable. If Nostr doesn’t make itself known, something else will fill that void. Let’s start this conversation.
-
 @ f6488c62:c929299d
2025-05-15 04:04:24
@ f6488c62:c929299d
2025-05-15 04:04:24วันที่ 8 เมษายน 2568 (2025) ทีมนักพัฒนา Solana (@solana_devs) ได้ประกาศเปิดตัว Confidential Balances Token Extensions บน Solana Mainnet
ซึ่งเป็นมาตรฐานโทเค็นที่ใช้เทคโนโลยี Zero-Knowledge Proofs (ZKPs) เป็นครั้งแรก เพื่อเพิ่มความเป็นส่วนตัว (privacy) และการปฏิบัติตามกฎระเบียบ (compliance) สำหรับการใช้งานในระดับสถาบัน โดยยังคงรักษาความเร็วในการยืนยันธุรกรรมที่ต่ำกว่า 1 วินาที (sub-second finality) อันเป็นจุดเด่นของ Solana
Confidential Balances เป็นชุดของ Token Extensions (ส่วนขยายของโทเค็น) ที่ออกแบบมาเพื่อเพิ่มความเป็นส่วนตัวให้กับธุรกรรมบนบล็อกเชน Solana โดยใช้เทคโนโลยี Zero-Knowledge Proofs (ZKPs) และ homomorphic encryption เพื่อปกปิดข้อมูลที่ละเอียดอ่อน เช่น จำนวนโทเค็นที่โอน, การสร้าง (mint), การเผา (burn), และค่าธรรมเนียม (fees) ในขณะที่ยังคงรักษาความโปร่งใสที่จำเป็นสำหรับการปฏิบัติตามกฎระเบียบของสถาบัน ฟีเจอร์นี้พัฒนาต่อยอดจาก Confidential Transfers ซึ่งเปิดตัวครั้งแรกในโปรแกรม Token2022 ของ Solana เมื่อเดือนมิถุนายน 2567 (2024) โดย Confidential Balances ขยายขอบเขตการใช้งานให้ครอบคลุมมากขึ้นและตอบโจทย์ทั้งผู้ใช้ทั่วไปและองค์กร คุณสมบัติหลักของ Confidential Balances Confidential Balances ประกอบด้วยส่วนขยายโทเค็น 3 ส่วนหลัก ดังนี้: Confidential Transfers (การโอนแบบเป็นส่วนตัว)
ช่วยให้ผู้ใช้สามารถโอนโทเค็นโดยซ่อน จำนวนเงินที่โอน จากสาธารณะ แต่ที่อยู่ของกระเป๋าเงิน (wallet addresses) ยังคงมองเห็นได้ใช้ homomorphic encryption และ ZKPs เพื่อให้ระบบสามารถตรวจสอบความถูกต้องของธุรกรรมได้โดยไม่ต้องเปิดเผยจำนวนเงิน
เหมาะสำหรับการใช้งานที่ต้องการความเป็นส่วนตัว เช่น การโอนเงินระหว่างธุรกิจ (B2B payments) หรือการจ่ายเงินเดือน (payroll)
Confidential Transfer Fees (ค่าธรรมเนียมแบบเป็นส่วนตัว)
ปกปิดข้อมูลเกี่ยวกับ ค่าธรรมเนียม ที่เกิดขึ้นในธุรกรรมช่วยให้ธุรกรรมทั้งหมด รวมถึงการหักค่าธรรมเนียม มีความเป็นส่วนตัวมากขึ้น
Confidential Mint and Burn (การสร้างและเผาโทเค็นแบบเป็นส่วนตัว)
อนุญาตให้ผู้ออกโทเค็น (token issuers) สามารถ สร้าง (mint) หรือ เผา (burn) โทเค็นโดยไม่เปิดเผยจำนวนโทเค็นทั้งหมดเหมาะสำหรับโปรเจกต์ที่ต้องการควบคุมปริมาณโทเค็นอย่างเป็นส่วนตัว เช่น Stablecoin หรือโทเค็นที่ใช้ในระบบการเงิน
เทคโนโลยีที่อยู่เบื้องหลัง Confidential Balances ใช้เทคโนโลยี cryptographic ขั้นสูง ดังนี้: Zero-Knowledge Proofs (ZKPs): ZKPs ช่วยให้ระบบสามารถพิสูจน์ความถูกต้องของธุรกรรม (เช่น จำนวนเงินที่โอนเพียงพอหรือไม่) โดยไม่ต้องเปิดเผยข้อมูลที่ละเอียดอ่อน ตัวอย่างเช่น ผู้ใช้สามารถพิสูจน์ว่าได้โอนเงินจำนวนหนึ่งโดยไม่ต้องบอกว่าโอนเท่าไหร่
Homomorphic Encryption: การเข้ารหัสแบบโฮโมมอร์ฟิกช่วยให้ระบบสามารถคำนวณข้อมูลที่เข้ารหัสได้โดยตรง โดยไม่ต้องถอดรหัส ซึ่งรักษาความเป็นส่วนตัวของข้อมูลในทุกขั้นตอนของธุรกรรม
ElGamal Encryption: ใช้ในการเข้ารหัสยอดคงเหลือและจำนวนโอน เพื่อให้ข้อมูลเหล่านี้มองเห็นได้เฉพาะผู้ที่มีกุญแจถอดรหัส (เช่น ผู้รับหรือผู้ตรวจสอบที่ได้รับอนุญาต)
Auditor Keys: เพื่อให้สอดคล้องกับกฎระเบียบ สถาบันสามารถใช้ "Auditor Keys" เพื่อตรวจสอบข้อมูลธุรกรรมที่เข้ารหัสได้เมื่อจำเป็น เช่น เพื่อปฏิบัติตามกฎหมายป้องกันการฟอกเงิน (AML) หรือการรายงานภาษี
ประโยชน์และการใช้งาน Confidential Balances ออกแบบมาเพื่อตอบโจทย์ทั้งผู้ใช้ทั่วไปและองค์กร โดยมีประโยชน์หลักดังนี้: เพิ่มความเป็นส่วนตัวโดยไม่สูญเสียประสิทธิภาพ
รักษาความเร็วในการยืนยันธุรกรรม (sub-second finality) และค่าธรรมเนียมที่ต่ำ (มักต่ำกว่า $0.01) ซึ่งเป็นจุดแข็งของ Solanaเปรียบเทียบกับ Ethereum ที่ใช้ zkRollups ซึ่งมีต้นทุนสูงกว่าและช้ากว่า
เหมาะสำหรับการใช้งานในระดับสถาบัน
รองรับการใช้งานในระบบการเงินที่ต้องการความเป็นส่วนตัว เช่น:
Payroll Systems: การจ่ายเงินเดือนที่ไม่เปิดเผยจำนวนเงินB2B Payments: การโอนเงินระหว่างธุรกิจที่ต้องการความลับ
Merchant Payment Solutions: การชำระเงินที่ปกป้องข้อมูลลูกค้า
Privacy-Preserving dApps: แอปพลิเคชัน DeFi หรือแอปผู้บริโภคที่เน้นความเป็นส่วนตัว
การปฏิบัติตามกฎระเบียบ
Auditor Keys ช่วยให้หน่วยงานกำกับดูแลสามารถตรวจสอบธุรกรรมได้ตามความจำเป็น โดยไม่กระทบต่อความเป็นส่วนตัวของผู้ใช้ทั่วไปทำให้ Solana เป็นตัวเลือกที่น่าสนใจสำหรับสถาบันการเงินที่ต้องปฏิบัติตามกฎหมาย AML, CTF (Counter-Terrorist Financing) หรือการรายงานภาษี
การเข้าถึงที่ง่ายขึ้นสำหรับผู้ใช้ทั่วไป
Solana มีแผนพัฒนา JavaScript-based ZK proof libraries ภายในปี 2568 ซึ่งจะช่วยให้กระเป๋าเงิน (wallets) เช่น Phantom หรือ Backpack สามารถรวมฟีเจอร์ Confidential Balances ได้ผู้ใช้จะสามารถสร้างและตรวจสอบ ZK proofs ได้โดยตรงจากเบราว์เซอร์หรือแอปมือถือ โดยไม่ต้องพึ่งพาเซิร์ฟเวอร์ภายนอก
สถานะการใช้งานในปัจจุบัน การใช้งานสำหรับนักพัฒนา:
Confidential Balances พร้อมใช้งานแล้วในสภาพแวดล้อม Rust-based backends สำหรับการพัฒนาแบบ server-sideรองรับ Wallets-as-a-Service (WaaS) สำหรับโซลูชัน custodial ซึ่งช่วยอำนวยความสะดวกสำหรับผู้ใช้ที่ไม่ต้องการจัดการกุญแจส่วนตัวเอง
dApps ที่ต้องการจัดการโทเค็นแบบเป็นส่วนตัวสามารถเริ่มใช้งานได้ทันที
ข้อจำกัดในปัจจุบัน:
กระเป๋าเงินสำหรับผู้ใช้ทั่วไป (เช่น Phantom) ยังไม่รองรับฟีเจอร์นี้แบบ nativeการพัฒนา JavaScript-based ZK proof libraries คาดว่าจะแล้วเสร็จในปลายปี 2568 ซึ่งจะทำให้การใช้งานง่ายขึ้นสำหรับผู้ใช้ทั่วไป
ตัวอย่างการใช้งานจริง:
โปรเจกต์ Agora Dollar (Stablecoin) เป็นโปรเจกต์แรกที่ใช้ Confidential Transfers เพื่อพัฒนาระบบจ่ายเงินเดือนแบบเป็นส่วนตัวในระดับสถาบันRange Security ได้สาธิตการโอน USDT แบบเป็นส่วนตัวโดยใช้ Confidential Transfers เพื่อแสดงศักยภาพของฟีเจอร์นี้
ผลกระทบต่อ Solana และการยอมรับในวงกว้าง การยอมรับจากสถาบัน
Pat Zhang หัวหน้าฝ่ายวิจัยของ WOO X ระบุว่า Confidential Balances อาจช่วยเพิ่มการยอมรับ Solana ในหมู่สถาบันการเงิน เนื่องจากสามารถให้ความเป็นส่วนตัวที่สอดคล้องกับกฎระเบียบได้การติดตามตัวชี้วัด เช่น การสร้างโทเค็น (token minting), กิจกรรมบนเชน (on-chain metrics), และการใช้งานกระเป๋าเงินของสถาบัน จะเป็นกุญแจในการวัดความสำเร็จของฟีเจอร์นี้
ข้อได้เปรียบด้านต้นทุนและความเร็ว
ค่าธรรมเนียมของ Solana ที่ต่ำ (ต่ำกว่า $0.01) และความเร็วในการทำธุรกรรม ทำให้ฟีเจอร์ความเป็นส่วนตัวนี้เข้าถึงได้ง่ายกว่าบล็อกเชนอื่น เช่น Ethereum ที่ใช้ zkRollups ซึ่งมีต้นทุนสูงกว่าความท้าทาย
เนื่องจากฟีเจอร์นี้เพิ่งเปิดตัวได้เพียง 1 เดือน (นับถึงวันที่ 15 พฤษภาคม 2568) ยังยากที่จะประเมินผลกระทบต่อการยอมรับ Solana ในวงกว้างความเสี่ยงด้านความปลอดภัย เช่น การใช้ Confidential Balances ในกลยุทธ์การหลอกลวง (rug pulls) ถูกกล่าวถึงโดย Scott Hague จาก RugCheck ซึ่งแนะนำให้แอปพลิเคชันในระบบนิเวศระบุโทเค็นที่ใช้ฟีเจอร์นี้อย่างชัดเจน
เปรียบเทียบกับ Confidential Transfers เดิม Confidential Transfers (Token2022, มิถุนายน 2567):
มุ่งเน้นที่การโอนโทเค็นโดยซ่อนจำนวนเงินเป็นฟีเจอร์เดี่ยวที่เน้นการโอนเพียงอย่างเดียว
Confidential Balances (เมษายน 2568):
ขยายขอบเขตให้ครอบคลุมการโอน, ค่าธรรมเนียม, การสร้าง และการเผาโทเค็นเป็นชุดของส่วนขยายที่ทำงานร่วมกันเพื่อให้ความเป็นส่วนตัวที่ครอบคลุมมากขึ้น
เพิ่ม Auditor Keys เพื่อรองรับการตรวจสอบสำหรับสถาบัน
อนาคตของ Confidential Balances การพัฒนา JavaScript ZK Libraries: คาดว่าจะเปิดตัวในปลายปี 2568 ซึ่งจะช่วยให้กระเป๋าเงินและ dApps สามารถรวมฟีเจอร์นี้ได้ง่ายขึ้น ตัวอย่างเช่น ผู้ใช้จะสามารถสร้าง ZK proofs ได้โดยตรงจากกระเป๋าเงินบนมือถือหรือเบราว์เซอร์
การรวมเข้ากับกระเป๋าเงินยอดนิยม: กระเป๋าเงินอย่าง Phantom และ Backpack มีแนวโน้มที่จะเพิ่มการรองรับ Confidential Balances ซึ่งจะทำให้ผู้ใช้ทั่วไปสามารถเข้าถึงฟีเจอร์นี้ได้โดยไม่ต้องมีความรู้ด้านเทคนิค
การใช้งานในวงกว้าง:
ระบบการจ่ายเงินเดือนแบบเป็นส่วนตัวการโอนเงิน B2B ที่ต้องการความลับ
แอปพลิเคชัน DeFi และแอปผู้บริโภคที่เน้นความเป็นส่วนตัว
Stablecoin ที่ต้องการความเป็นส่วนตัว เช่น โปรเจกต์ของ Agora
สรุป Confidential Balances Token Extensions เป็นก้าวสำคัญของ Solana ในการเพิ่มความเป็นส่วนตัวให้กับบล็อกเชน โดยใช้เทคโนโลยี ZKPs และ homomorphic encryption เพื่อปกป้องข้อมูลธุรกรรม ในขณะที่ยังคงรักษาความเร็วและต้นทุนต่ำที่เป็นจุดเด่นของ Solana ฟีเจอร์นี้ไม่เพียงแต่ตอบโจทย์ผู้ใช้ทั่วไปที่ต้องการความเป็นส่วนตัว แต่ยังดึงดูดสถาบันการเงินด้วยการปฏิบัติตามกฎระเบียบผ่าน Auditor Keys ในอนาคต การพัฒนา JavaScript ZK libraries และการรวมเข้ากับกระเป๋าเงินยอดนิยมจะทำให้ Confidential Balances เข้าถึงได้ง่ายขึ้น ซึ่งอาจผลักดันให้ Solana กลายเป็นแพลตฟอร์มชั้นนำสำหรับทั้งแอปพลิเคชันผู้บริโภคและการใช้งานในระดับองค์กร แหล่งข้อมูล:
โพสต์จาก @solana_devs และ @heliuslabs บน Xบทความจาก BeInCrypto, The Block, CryptoSlate, และ The Defiant
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ 9223d2fa:b57e3de7
2025-05-15 02:36:17
@ 9223d2fa:b57e3de7
2025-05-15 02:36:1715,432 steps
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ da931929:e4097d1a
2025-05-15 02:04:26
@ da931929:e4097d1a
2025-05-15 02:04:26Bottom-up Load-balancing for Nostr Relays
Goal: protect your relay by distributing clients more evenly across all relays without top-down coordination.
The problem
Nostr relays are a public good with the costs borne by benevolent volunteers running them. So far this system has been robust, supporting tens of thousands of active users per month. There is some low-key evidence of strain on these servers (see below) and overload could become a bigger problem as the network grows, attracts spammers, griefers, and other bad actors. It could become expensive to run the most popular relays even under ideal conditions with conscientious users.
The main strategies employed by relays to mitigate overload currently are a) throttling requests b) pre-set PoW c) authentication of some form, with throttling being common on popular servers. Throttling is an opaque strategy where client apps only receive the kill signal once they have been throttled. Pre-set PoW is exclusionary to most clients that don't implement it, and authentication is centralizing.
The current strategy employed by clients for selecting relays is for client apps to choose a set of default relays, and for users to modify those defaults manually in the UI. This results in natural aggregation of clients on the more popular relays. This concentrates load on a smaller number of relays and is centralizing.
A solution
A solution that helps both clients and relays is to make the relay overload signal legible.
Our proposal is simple:
- Relay software measures common load utilization percentage metrics like cpu, memory, and disk.
- Overloaded relays publish their current load expressed as a proof-of-work requirement (NIP-11).
- Clients upon seeing the proof-of-work requirement can do the PoW or switch relays (NIP-13, NIP-01).
This sets up a basic PoW market where "prices" help "consumers" decide where to allocate their "capital" (events with proof-of-work tokens). The likely effect is that clients will automatically re-distribute their traffic away from "expensive" overloaded relays towards "cheap" underloaded relays, making the entire network healthier.
The new thing here is tying PoW to load. Existing NIPs cover most of the PoW part of the soultion. NIP-11 covers publishing of PoW requirements by relays. NIP-13 and NIP-01 cover clients performing PoW and relays reacting to it.
A pleasant side-effect of using PoW as the load signal is that would-be spammers are forced to pay an actual cost in the form of energy expenditure and hardware.
How to participate
Participation is opt-in. Any relay or client can participate in this scheme if they want to try it out, or ignore it if they don't. It doesn't require large scale changes to the protocol.
Relay implementation
To participate in this protocol relays would make these changes:
- Collect load metrics.
- Publish PoW requirements (NIP-11).
- Check PoW on incoming client events (NIP-13, NIP-01).
Collecting load metrics is straightforward. Relays can collect CPU loadavg, memory usage (averaged), and disk utilization as percentages. We suggest the final load percentage value should be:
max(cpu%, mem%, disk%)as a starting point. The reason for usingmax()is that problems arise if any of your resources is exhausted, so we should rely on the most exhausted resource as the actual load value.PoW required can be calculated (see section below) by using a sensible starting point for tolerable load - the
zero-PoW-loadpoint. Amax-bitsdiffculty can be specified for the 100% load point. Thezero-PoW-loadvalue is the load percentage up until which the relay is comfortable offering connections "free" without requring any PoW. This situation would be the same as it is currently with clients able to freely connect to most relays. Once thezero-PoW-loadis reached the server would start publishing a number of bits of PoW required using NIP-11. The PoW required would scale up with the load experienced. Of coursezero-PoW-loadcan be set low to facilitate early PoW market signals.New metrics that relays care about can be added to the calculation in future without clients caring. Other metrics could be used such as percent of available TCP/websocket connection slots used, or actual server rental costs vs. maximum cost a volunteer will bear.
Validating PoW on incoming client events is something that has already been discussed and implemented in relays. See NIPs 11, 13, and 01.
PoW Required Calculation
zero_pow_loadis a setting for the minimum load percentage where PoW should kick in with 1 bit of PoW. 80% could be a sensible starting point. Operators of popular relays can use their own historical data to determine this.max_bitsis set to the highest PoW clients will have to do when server load goes near 100%. This can be calibrated to some value like 1 hour of PoW on an average modern device. It's not expected clients will actually perform this but it sets the scale, and it should prevent highly resourced spammers from 100% utilization of any relay.current_loadis the computed maximum of all of the load metric percentages gathered.
Then the formula for calculating the required PoW bits is:
pow_bits_required = max_bits * max(0, (current_load - zero_pow_load) / (100 - zero_pow_load))Since PoW increases logarithmically (each bit being exponentially harder than the last) some scaling function may be required to smooth this off.
Client implementation
These are the changes clients would make to participate in this protocol.
- Select relays based on PoW (favour PoW-cheap + known reliable relays).
- Do PoW if connecting to overloaded servers (NIP-11 and NIP-13).
Selecting relays for the user then might mean keeping a larger list of potential default relays and selecting a subset at setup time based on PoW requirements. It might also mean actively monitoring for high-PoW relays and switching away if a relay is frequently expensive.
It is in a client's best interest to select a low-PoW underloaded set of relays to publish to, whilst still favouring known-reliable relays. If the whole network becomes loaded then PoW acts as a deterrent for non-critical use and spammers. Only the most commited clients and users will participate. It can also be a transparent signal to the community that more relays are required.
Addenda
So that's the main specification of the scheme. The following are related addenda.
Evidence of strain
Some random low-key evidence of strain on relays, and worries about the costs of running them.
nostr:note1kp57fvd8jz6639g86ugv5zy4q2sn52mz30kqp6xwgtlgph44q22stt7hkk
nostr:note19cp5rzvrmu7gc7n6czv8650wlyc355yffmy6amxtmd3pmut4umcqsr9dm4
nostr:note16vmlqsucqqgyjuac66wvpux903xrw5gea4wewtvz9ufhy5s8y83qscu5wv
TODO: sample some nostr events/users randomly from the firehose and get stats on relay centralization.
More weird PoW ideas
One thing not covered in NIPs is PoW-on-connect which could help in future if there are malicious clients camping on websockets.
Another idea is building PoW into npubs, similar to vanitygen, which would put some skin-in-the-game onto users when creating keys. Some relays may choose only to service high PoW npubs that have proven their commitment to the network and protocol.
On resource rationing
Some ways to ration unexpectedly demanded goods in an emergency:
(1) market prices ("price gouging") (2) waiting in line (3) centrally planned rationing (4) don't ration: just let the resource run out
Market prices are a least-worst business-as-usual option.
-
 @ 58537364:705b4b85
2025-05-15 01:46:43
@ 58537364:705b4b85
2025-05-15 01:46:43“พระอาจารย์คะ หนูไม่ได้อะไรนะคะ ก็ในเมื่อพระพุทธศาสนามีแก่นคำสอนอยู่แล้ว ถ้าหนูคิดว่าควรจะลดพวกวัด หรืออะไรต่างๆ ลง นี่เป็นบาปมั้ยคะ?”
“เจริญพร ตอนหนูกินกล้วยนี่กินเปลือกหรือกินผลกล้วย ?” ”กินผลกล้วยค่ะ” “เหรอ…แล้วก่อนจะกินกล้วยหนูต้องปอกก่อนมั้ย ?” เด็กสาวหน้าตาสะอาดสะอ้าน พยักหน้าหงึก~
“ปอกทำไมล่ะ?” “ก็เปลือกมันกินไม่ได้หนิคะ” “อ๋อ…อย่างนั้นเปลือกก็ไม่มีประโยชน์เลยใช่มั้ย?” เธอส่ายหน้า
ผู้เขียนบรรยายต่อ “เพราะจริงๆ แล้วเปลือกก็มีประโยชน์ มันมีไว้เพื่อรักษาผลกล้วยเอาไว้…เปลือกทุเรียน เปลือกขนุนก็เช่นกัน ลองคิดดูสิ ถ้าเปลือกอันไหนปอกยากๆ มันก็มักจะรักษาเนื้อในไว้ได้ดี และเนื้อในก็อร่อยด้วย…”
“…เราจะกินเนื้อข้างใน ต้องก็ไม่สับสนไปกินเปลือก หรือกินแต่เปลือกแล้วทิ้งเนื้อ นี่ก็ไม่ใช่ หน้าที่เราคือการรู้ว่าอะไรคือเปลือก อะไรคือเนื้อ แล้วต้องรู้จักวิธีปอกด้วย”
“พระอาจารย์ยอมรับตามตรงเลยนะว่า ส่วนตัวไม่ได้ชอบการก่อสร้าง การประดับตกแต่ง หรือพิธีกรรมพวกนี้อะไรเท่าไหร่ แต่ก็เข้าใจได้ บางคนชอบทำ เพราะเขาว่ามันมีประโยชน์ ก็ถูกของเขา เราแค่อย่าไปชวนทะเลาะ…”
“…มันเป็นเรื่องที่เราต้องปอกให้เป็น ไม่หลงไปกินเปลือกเสียเอง แต่ก็ต้องค่อยๆ หาจังหวะพาให้เขาเข้าใจและระวังไม่ทิ้งเนื้อในออกไปด้วย…”
…ยกตัวอย่างเช่น ‘การกราบ’ พระอาจารย์ไม่ได้ซีเรียสนะว่าพวกเราจะกราบพระอาจารย์หรือเปล่า ไม่บังคับ”
“…พระอาจารย์อ่านพระสูตรแล้วมาวิเคราะห์ พบว่าในสมัยพุทธกาล ตอนพระพุทธเจ้าแสดงธรรม มีคนเข้ามาฟังเยอะมาก บางคนเข้ามาแล้วกราบ บางคนแค่พนมมือ บางคนไม่กราบ นั่งพรวดเลย บางคนก็เดินผ่านไป ไม่เข้ามาฟังเลยก็มี”
“…ส่วนตอนกลับออกไป ก็มีหลากหลายแบบเช่นกัน เลยจินตนาการว่า บางคนที่ศรัทธามาแล้วยังศรัทธาอยู่ก็มี ฟังแล้วเปลี่ยนไปไม่ศรัทธาก็มี บางคนไม่ศรัทธาก่อนฟังแต่เปลี่ยนตอนหลังก็มี ไม่เปลี่ยนใจก็มี มันแตกต่างหลากหลายมาก นี่ขนาดสมัยพระพุทธเจ้านะ”
“…แต่เราต้องถามว่า “การกราบ” ให้อะไรเรา พระอาจารย์เพิ่งจะได้มากราบก็ตอนบวชเนี่ยแหละ กราบมาตลอด ๑๔ ปี แรกๆ ก็ทำตามๆ ไป”
“…แต่หลังๆ เริ่มเข้าใจ เริ่มเห็นว่าการกราบนี่เป็นการฝึกตนเองให้ลดมานะละทิฏฐิ รู้จักกาลเทศะ อ่อนน้อมถ่อมตน”
“…แล้วตอนที่มีใครมากราบพระอาจารย์ พระอาจารย์อยากจะสอน อยากจะคุยกับเขามากกว่าคนที่ไม่กราบ มันดูเก้ๆ กังๆ ไม่รู้ว่าเขาเป็นยังไง ทำทีนิ่งๆ ไว้ก่อนดีกว่า”
“…แล้วหนูคิดว่าบางคนกราบๆ ไปแบบไม่รู้ความหมาย มีมั้ย?” เด็กน้อยพยักหน้า
“ใช่มั้ย…พระอาจารย์เลยคิดว่า การกราบก็ดี พิธีกรรมก็ดี วัดวาอารามก็ดี ไม่ใช่เนื้อหาสูงสุด ไม่ใช่แก่น แต่มันก็มีความหมาย พาให้เราเข้าถึงประโยชน์ที่สูงสุดที่อยู่ซ่อนในนั้น เป็นหน้าที่ที่เราต้องทำความเข้าใจ หากเราอยากจะเข้าใจมัน”
“พระอาจารย์เชื่อมั่นว่า ศาสนาที่แท้ไม่ได้อยู่ในวัตถุ สิ่งของ เพราะไม่เช่นนั้นแล้ว ‘บูโรพุทโธ’ ที่เป็นศาสนสถานที่ใหญ่ที่สุดในโลก มีเจดีย์ละลานตา จะต้องมีพระ มีชาวพุทธจำนวนมากตามกัน แต่เดี๋ยวนี้เป็นอย่างไรบ้าง? รู้มั้ย?“ เด็กน้อยส่ายหน้า
“…ตอนนี้ เป็นเพียงสถานที่ท่องเที่ยว ไม่มีพระอยู่อาศัยแล้ว”
“…ที่หนูว่าจะลดวัดต่างๆ ลง นี่หนูคิดว่าจะเอาไปทำอะไรเหรอ?” “คืออย่างเอาไปเป็นสวนสาธารณะอย่างเนี่ยน่ะค่ะ”
“ดีนะ…เข้าท่า พระอาจารย์ชอบ คนอื่นจะได้มาใช้กันเยอะๆ มีต้นไม้ มีสัตว์ต่างๆ ด้วย ทุกคนจะได้สบายใจ” เด็กน้อยตาวาว
“แต่เราสามารถทำให้วัดมีต้นไม้เยอะๆ ได้มั้ยล่ะ ทำวัดให้เหมือนสวนสาธารณะไง ไอเดียดีมั้ย?” รอยยิ้มเด็กน้อยผุดขึ้น
“…ซึ่งถึงแม้พระอาจารย์ไม่อยากให้เราติดอยู่ที่วัตถุหรือรูปแบบพิธีกรรมขนาดไหน พระอาจารย์ก็เห็นประโยชน์ของมันอยู่นะ หนูดูนั่นสิ !”
ปลายนิ้วชี้ไปที่ ‘กล่องไม้แกะสลัก’ เด็กๆ ทั้งห้องหันหน้าไปมองเป็นตาเดียว
“…กล่องนี้อาจจะเป็นกล่องไม้ธรรมดาๆ ไม่มีค่าอะไร แต่พอแกะสลักปุ๊บ ดูมีค่าขึ้นมาทันทีเลย ดูแตกต่างจากกล่องอื่นๆ ช่างที่ทำก็ต้องมีฝีมือ มีเวลา ทุ่มเทเอาใจใส่กว่าจะเกิดผลงานเช่นนี้ขึ้น
“…ถ้ามีกล่องไม้หลายๆ กล่อง แล้วจะต้องเลือกเก็บไว้สักหนึ่งอัน กล่องนี้คงเป็นกล่องแรกๆ ที่ถูกเลือกก่อน
“…นี่เรียกว่า ‘คุณค่าของความสวยงาม’ พวกโบสถ์ เจดีย์ สถานที่สวยๆ งามๆ คนก็จะมาดูแลรักษาก่อน ทำความสะอาด เก็บรักษาการใช้งานที่จะเกิดขึ้นภายในอาคารเหล่านั้น พระอาจารย์เดาว่า แรกเริ่มเดิมทีธรรมเนียมนิยมในการสร้างวัดต่างๆ ให้สวยงาม คงเป็นแบบนี้”
“อีกนิดนะ เรื่องบุญหรือบาป ชวนหนูทำความเข้าใจความหมายก่อน บุญ แปลว่า การชำระใจให้สะอาด บาป แปลว่า การทำให้จิตใจตกต่ำ เศร้าหมอง”
“การที่หนูอยากจะทำสวนสาธารณะ นี่บุญหรือบาป?” “บุญค่ะ”
“ถ้าหนูรู้สึกรำคาญ อยากจะทุบวัดให้หมดๆ ไป นี่บุญหรือบาป?” “บาปค่ะ”
“แล้วถ้าหนูกราบด้วยความเข้าใจ อยากจะฝึกตนเองให้อ่อนน้อมถ่อมตน พร้อมรับฟังธรรมะจากพระ นี่บุญหรือบาป?” “บุญค่ะ”
“การที่หนูกราบแบบขอไปที หลงๆ ลืมๆ ทำตามเพื่อนๆ ไป นี่บุญหรือบาป?” เด็กน้อยนิ่ง เหลือบตามองบน
“ยังไม่ชัดใช่มั้ย?” “ค่ะ“ เธอพยักหน้าแรง
“งั้นพระอาจารย์ก็ฝากหนูสังเกต ‘ใจ’ ตัวเองนะ ว่ามันเป็นยังไง บุญหรือบาป สะอาดหรือตกต่ำ ไม่ใช่แค่การกราบ แต่เป็นทุกๆ การกระทำ คำพูด และความคิดเลย”
“นี่พระอาจารย์ พอจะตอบคำถามหนูได้กี่เปอร์เซ็นต์?” “ร้อยเปอร์เซ็นต์ค่ะ” “เหรอ…โอเค ขอบคุณมากค่ะสำหรับคำถาม”
เด็กๆ พากันกราบแล้วเดินออกจากศาลาไป ผู้เขียนอาศัย “ตีเหล็กตอนร้อน” พิจารณาชื่นชมคำถามและคำตอบเมื่อสักครู่
คำถามของเด็กน้อยคนนี้ ไม่ใช่เด็กๆ เลย คำถามเธอเป็น ‘ผู้ใหญ่’ มากกว่าผู้ใหญ่หลายคนที่เคยถามมาเสียอีก
มันทั้งความคมคาย ละเอียดและมีชั้นเชิง น้ำเสียงชัดเจน มั่นใจ เลือกแสดงออกอย่างกล้าหาญพร้อมไปกับเจือความนอบน้อมอยู่ในที ถามได้ตรงประเด็น เกิดประโยชน์ สร้างรอยหยักในสมองให้ทั้งผู้ถูกถามและผู้ร่วมฟัง
ระหว่างฟัง เธอมองหน้าและคิดตาม มีปฏิกิริยาตอบสนอง ช่วยให้เกิดการร่วมเรียนรู้ไปด้วยกัน เป็นผู้ฟังที่ดีไม่ชัดจังหวะ และที่สำคัญรอยยิ้มและแววตาของเธอได้กระจายไปให้กำลังใจเพื่อนๆ ในห้องด้วย
และนี่ มันทำให้ผู้ตอบ รู้สึกดี ภูมิใจที่ได้มานั่งอยู่ตรงนี้ ในวันนี้ เวลานี้
ดีใจจริงๆ ที่ยังมีเด็กที่มีจิตใจที่งดงาม คิดถึงธรรมชาติ และคิดทำประโยชน์สุขให้ผู้อื่นอยู่ แถมเธอยังรู้และสนใจใน “พุทธะ” ที่เป็นแก่นสารสาระที่แท้จริงอีกด้วย
“มันน่าภูมิใจจริงๆ ที่ได้รับรู้ว่าธรรมะกำลังเคลื่อนไปสู่คนรุ่นหลัง จริงมั้ยครับ?”
ผู้เขียนไม่ได้ถามใคร ได้แต่หันไปมองรูปปั้นหินอ่อนลักษณะคล้ายคนที่วางไว้ข้างหลัง น้อมระลึกถึงคุณของพระพุทธองค์ ผู้เป็นบรมครู ไม่เสื่อมคลาย
อาศรมขันติสาร บ้านไม้ที่เขาเรียกกุฏิ ๑๕ มิถุนายน ๒๕๖๖ แหล่งที่มา #Phramaha Fookij Jutipanyo
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ 08f96856:ffe59a09
2025-05-15 01:22:34
@ 08f96856:ffe59a09
2025-05-15 01:22:34เมื่อพูดถึง Bitcoin Standard หลายคนมักนึกถึงภาพโลกอนาคตที่ทุกคนใช้บิตคอยน์ซื้อกาแฟหรือของใช้ในชีวิตประจำวัน ภาพแบบนั้นดูเหมือนไกลตัวและเป็นไปไม่ได้ในความเป็นจริง หลายคนถึงกับพูดว่า “คงไม่ทันเห็นในช่วงชีวิตนี้หรอก” แต่ในมุมมองของผม Bitcoin Standard อาจไม่ได้เริ่มต้นจากการที่เราจ่ายบิตคอยน์โดยตรงในร้านค้า แต่อาจเริ่มจากบางสิ่งที่เงียบกว่า ลึกกว่า และเกิดขึ้นแล้วในขณะนี้ นั่นคือ การล่มสลายทีละน้อยของระบบเฟียตที่เราใช้กันอยู่
ระบบเงินที่อิงกับอำนาจรัฐกำลังเข้าสู่ช่วงขาลง รัฐบาลทั่วโลกกำลังจมอยู่ในภาระหนี้ระดับประวัติการณ์ แม้แต่ประเทศมหาอำนาจก็เริ่มแสดงสัญญาณของภาวะเสี่ยงผิดนัดชำระหนี้ อัตราเงินเฟ้อกลายเป็นปัญหาเรื้อรังที่ไม่มีท่าทีจะหายไป ธนาคารที่เคยโอนฟรีเริ่มกลับมาคิดค่าธรรมเนียม และประชาชนก็เริ่มรู้สึกถึงการเสื่อมศรัทธาในระบบการเงินดั้งเดิม แม้จะยังพูดกันไม่เต็มเสียงก็ตาม
ในขณะเดียวกัน บิตคอยน์เองก็กำลังพัฒนาแบบเงียบ ๆ เงียบ... แต่ไม่เคยหยุด โดยเฉพาะในระดับ Layer 2 ที่เริ่มแสดงศักยภาพอย่างจริงจัง Lightning Network เป็น Layer 2 ที่เปิดใช้งานมาได้ระยะเวลสหนึ่ง และยังคงมีบทบาทสำคัญที่สุดในระบบนิเวศของบิตคอยน์ มันทำให้การชำระเงินเร็วขึ้น มีต้นทุนต่ำ และไม่ต้องบันทึกทุกธุรกรรมลงบล็อกเชน เครือข่ายนี้กำลังขยายตัวทั้งในแง่ของโหนดและการใช้งานจริงทั่วโลก
ขณะเดียวกัน Layer 2 ทางเลือกอื่นอย่าง Ark Protocol ก็กำลังพัฒนาเพื่อตอบโจทย์ด้านความเป็นส่วนตัวและประสบการณ์ใช้งานที่ง่าย BitVM เปิดแนวทางใหม่ให้บิตคอยน์รองรับ smart contract ได้ในระดับ Turing-complete ซึ่งทำให้เกิดความเป็นไปได้ในกรณีใช้งานอีกมากมาย และเทคโนโลยีที่น่าสนใจอย่าง Taproot Assets, Cashu และ Fedimint ก็ทำให้การออกโทเคนหรือสกุลเงินที่อิงกับบิตคอยน์เป็นจริงได้บนโครงสร้างของบิตคอยน์เอง
เทคโนโลยีเหล่านี้ไม่ใช่การเติบโตแบบปาฏิหาริย์ แต่มันคืบหน้าอย่างต่อเนื่องและมั่นคง และนั่นคือเหตุผลที่มันจะ “อยู่รอด” ได้ในระยะยาว เมื่อฐานของความน่าเชื่อถือไม่ใช่บริษัท รัฐบาล หรือทุน แต่คือสิ่งที่ตรวจสอบได้และเปลี่ยนกฎไม่ได้
แน่นอนว่าบิตคอยน์ต้องแข่งขันกับ stable coin, เงินดิจิทัลของรัฐ และ cryptocurrency อื่น ๆ แต่สิ่งที่ทำให้มันเหนือกว่านั้นไม่ใช่ฟีเจอร์ หากแต่เป็นความทนทาน และความมั่นคงของกฎที่ไม่มีใครเปลี่ยนได้ ไม่มีทีมพัฒนา ไม่มีบริษัท ไม่มีประตูปิด หรือการยึดบัญชี มันยืนอยู่บนคณิตศาสตร์ พลังงาน และเวลา
หลายกรณีใช้งานที่เคยถูกทดลองในโลกคริปโตจะค่อย ๆ เคลื่อนเข้ามาสู่บิตคอยน์ เพราะโครงสร้างของมันแข็งแกร่งกว่า ไม่ต้องการทีมพัฒนาแกนกลาง ไม่ต้องพึ่งกลไกเสี่ยงต่อการผูกขาด และไม่ต้องการ “ความเชื่อใจ” จากใครเลย
Bitcoin Standard ที่ผมพูดถึงจึงไม่ใช่การเปลี่ยนแปลงแบบพลิกหน้ามือเป็นหลังมือ แต่คือการ “เปลี่ยนฐานของระบบ” ทีละชั้น ระบบการเงินใหม่ที่อิงอยู่กับบิตคอยน์กำลังเกิดขึ้นแล้ว มันไม่ใช่โลกที่ทุกคนถือเหรียญบิตคอยน์ แต่มันคือโลกที่คนใช้อาจไม่รู้ตัวด้วยซ้ำว่า “สิ่งที่เขาใช้นั้นอิงอยู่กับบิตคอยน์”
ผู้คนอาจใช้เงินดิจิทัลที่สร้างบน Layer 3 หรือ Layer 4 ผ่านแอป ผ่านแพลตฟอร์ม หรือผ่านสกุลเงินใหม่ที่ดูไม่ต่างจากเดิม แต่เบื้องหลังของระบบจะผูกไว้กับบิตคอยน์
และถ้ามองในเชิงพัฒนาการ บิตคอยน์ก็เหมือนกับอินเทอร์เน็ต ครั้งหนึ่งอินเทอร์เน็ตก็ถูกมองว่าเข้าใจยาก ต้องพิมพ์ http ต้องรู้จัก TCP/IP ต้องตั้ง proxy เอง แต่ปัจจุบันผู้คนใช้งานอินเทอร์เน็ตโดยไม่รู้ว่าเบื้องหลังมีอะไรเลย บิตคอยน์กำลังเดินตามเส้นทางเดียวกัน โปรโตคอลกำลังถอยออกจากสายตา และวันหนึ่งเราจะ “ใช้มัน” โดยไม่ต้องรู้ว่ามันคืออะไร
หากนับจากช่วงเริ่มต้นของอินเทอร์เน็ตในยุค 1990 จนกลายเป็นโครงสร้างหลักของโลกในสองทศวรรษ เส้นเวลาของบิตคอยน์ก็กำลังเดินตามรอยเท้าของอินเทอร์เน็ต และถ้าเราเชื่อว่าวัฏจักรของเทคโนโลยีมีจังหวะของมันเอง เราก็จะรู้ว่า Bitcoin Standard นั้นไม่ใช่เรื่องของอนาคตไกลโพ้น แต่มันเกิดขึ้นแล้ว
siamstr
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 04c915da:3dfbecc9
2025-03-26 20:54:33
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 04c915da:3dfbecc9
2025-03-25 17:43:44
@ 04c915da:3dfbecc9
2025-03-25 17:43:44One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ 9223d2fa:b57e3de7
2025-04-15 02:54:00
@ 9223d2fa:b57e3de7
2025-04-15 02:54:0012,600 steps
-
 @ 502ab02a:a2860397
2025-05-15 01:03:05
@ 502ab02a:a2860397
2025-05-15 01:03:05วันหนึ่งเฮียนั่งอ่านบทความที่ชื่อว่า “Lactose, we need to talk” จากเว็บไซต์ของบริษัท Formo ผู้ผลิตชีสที่บอกว่า “ไม่ต้องมีวัว ก็อร่อยได้” ด้วยเทคโนโลยีหมักจุลินทรีย์อัจฉริยะจากเยอรมนี ที่เราเคยคุยเรื่องนี้กันไปแล้ว มันฟังดูเหมือนจะเป็นนวัตกรรมสุดเจ๋งที่เป็นมิตรกับทั้งโลกและกระเพาะ แต่พอเฮียไล่อ่านลึกลงไปเรื่อย ๆ กลับเจอกลยุทธ์ทางการตลาดที่ชวนให้ขมวดคิ้วไม่แพ้ชีสที่กินแล้วลิ้นฝาด ขอใส่ไอคอนการ์ตูนไว้หน่อยนะครับ จะได้ไม่ลายตา เพราะเราจะแบ่งช่วงมาวิเคราะห์กันเป็นข้อๆ
🍶 บทความของ Formo เปิดประโยคด้วยการตั้งคำถามถึง “การดื่มนมจากสัตว์ต่างสายพันธุ์” พร้อมยกประเด็นเรื่อง Lactose Intolerance ว่าเป็นสิ่งผิดปกติที่คนเรายังดื่มนมทั้งที่ร่างกายคนส่วนใหญ่ (โดยเฉพาะชาวเอเชียและแอฟริกัน) ไม่มีเอนไซม์ย่อยแลคโตสในวัยผู้ใหญ่
ฟังผ่าน ๆ ดูน่าเชื่อ แต่อย่าลืมว่า แลคโตสไม่ได้อยู่ในชีสทุกชนิด และหลายคนที่แพ้นมกลับกินชีสแท้ ๆ จากวัวได้สบายมาก โดยเฉพาะชีสหมักระยะยาว เช่น พาร์เมซาน เชดดาร์ หรือกูด้า ที่แลคโตสแทบเป็นศูนย์ ซึ่งต่างจากชีสทางเลือกที่ผลิตด้วยกระบวนการเร่ง ที่ไม่ได้หมักตามธรรมชาติ
ดังนั้น วัวไม่ผิด แค่ถูกพูดถึงในบริบทที่เสียเปรียบ การกล่าวหานมวัวด้วยข้อมูลเรื่อง lactose intolerance โดยไม่พูดถึงชีส aged ที่ไม่มีแลคโตสเลย เป็นการจงใจเบี่ยงข้อมูลเพื่อสร้างอารมณ์ด้านลบต่อ dairy ทั้งระบบ
🧬Formo บอกว่า คนที่ย่อยแลคโตสได้ในวัยผู้ใหญ่คือ “ผู้กลายพันธุ์” เพราะธรรมชาติไม่ตั้งใจให้เราดื่มนมหลังหย่านม ฟังดูเหมือนเน้นธรรมชาติ แต่เฮียอยากถามว่า “ถ้าอย่างนั้นการสวมแว่น การกินวิตามิน การตั้งไฟหุงข้าว คือการฝืนธรรมชาติหมดเลยหรือเปล่า?” หรือจะหนักกว่านั้น ให้ย้ำไปเลยไหมว่า การกินวิตามินซี คือการทรยศต่อวิวัฒนาการ เพราะในยุคดึกดำบรรพ์มนุษย์เคยสังเคราะห์วิตามินซีได้เอง ก่อนที่ความสามารถนี้จะสูญสลายไปเพราะร่างกายเลือกใช้ ยูริก ที่มีประสิทธิภาพกว่า ดังนั้น การมองยีนที่วิวัฒนาการเพื่อย่อยแลคโตสเป็น “กลายพันธุ์ผิดธรรมชาติ” นั้นย้อนแย้งกับหลักการวิวัฒนาการเอง “ยีนย่อยแลคโตส” ไม่ใช่ความผิดปกติ
🥬 ในบทความยังแนะนำว่า เราสามารถได้แคลเซียมจากคะน้า บรอกโคลี และเต้าหู้ โดยไม่ต้องพึ่งนมวัว เฮียอยากให้ใจเย็นแล้วคิดแบบไม่อคติ จริงอยู่ ผักพวกนี้มีแคลเซียม แต่ปริมาณที่กินต่อครั้ง กินง่าย และการดูดซึม (Bioavailability) แตกต่างกันมาก แถมผักใบเขียวพวกนี้ยังมี oxalate สูง ซึ่งไปจับกับแคลเซียมแล้วร่างกายดูดซึมไม่ได้ นี่ยังไม่พูดถึงว่าเต้าหู้ในบทความเป็นแบบเต้าหู้แข็งที่ทำจากแคลเซียมซัลเฟต ซึ่งเป็นแคลเซียมสังเคราะห์ ไม่ใช่แหล่งแร่ธาตุตามธรรมชาติแบบในนมวัวอยู่ดี การเปรียบเทียบแคลเซียมจากผัก ก็ไม่ต่างกับการเปรียบเทียบกล้วยกับปลา มันคนละเรื่องกัน
💔 ชูเรื่องสิว หัวใจ มะเร็ง แบบไม่มีบริบท Formo ยังโยงว่าการดื่มนมวัวสัมพันธ์กับสิว ปัญหาผิว โรคหัวใจ ไปจนถึงมะเร็งบางชนิด ซึ่งเป็นข้อมูลที่เคยถูกพูดถึงในงานวิจัยบางกลุ่ม แต่ ไม่มีฉันทามติทางวิทยาศาสตร์ชัดเจน และส่วนใหญ่ปัจจัยที่เกี่ยวข้องมักจะเป็นอาหารแปรรูป น้ำตาลสูง หรืออาหาร ultra-processed dairy ไม่ใช่นมดิบหรือชีสแท้จากฟาร์มจริง
🧀 แล้วชีสจาก Formo มีดีจริงรึเปล่า ก็ต้องยอมรับว่าเทคโนโลยี precision fermentation ที่ใช้เชื้อรา (เช่น Aspergillus oryzae) ผลิตโปรตีนคล้ายเคซีนของ Formo นั้นล้ำและน่าสนใจในแง่วิทยาศาสตร์ แต่ในแง่ ความสมบูรณ์ทางโภชนาการและความใกล้ชิดธรรมชาติ ยังห่างจากชีสแท้ที่เกิดจากนมและจุลินทรีย์ตามธรรมชาติแบบหลายช่วงตัว ชีสแท้ ๆ มีจุลินทรีย์โพรไบโอติกส์ กรดไขมันสายสั้น และวิตามินจากหญ้า เช่น K2 ที่เกิดจากวัวที่เลี้ยงด้วย grass-fed ซึ่งทั้งหมดนี้ Formo ยังเลียนแบบไม่ได้ เทคโนโลยีชีสไร้วัวอาจดูสะอาดและควบคุมได้ดีในห้องแล็บ แต่ยังไม่ใช่ "อาหารตามธรรมชาติ" ที่ร่างกายรู้จักมาตลอดวิวัฒนาการ
Formo ใช้บทความ “Lactose, we need to talk” เป็นเหมือนการ “ตั้งวงซุบซิบนินทาวัว” อย่างมีชั้นเชิง ด้วยการเอาข้อเท็จจริงมาครึ่งหนึ่ง แล้วผสมกลิ่นอารมณ์และความรู้สึกผิดเข้าไปอีกครึ่งหนึ่ง จนกลายเป็นการเล่าเรื่องที่ดูจริงใจแต่ซ่อนความตั้งใจขายของอยู่ข้างใน
เฮียไม่มีสิทธิ์บอกว่า Formo ดีหรือไม่ดีนะครับ แม้นวัตกรรมแบบนี้อาจมีที่ยืนในโลกอนาคต ไม่ว่าเราจะเลือกได้หรือไม่ได้ก็ตาม แต่ในปัจจุบันในฐานะผู้บริโภค เราควรฝึกการมองตลาดด้วยสมองและสัญชาตญาณ ไม่ใช่แค่ตามกระแสที่โจมตีวัวในขณะที่ยกย่องแล็บ
โลกทุกวันนี้มักใช้วิธีนี้เช่นกันครับ มันเป็นวิธีเดิมๆ ที่ได้ผลเสมอ ดังนั้นปัญหาจึงไม่ได้อยู่ที่ว่าพวกเขาจะพูดด้านเดียวบ่อยแค่ไหน เพราะจุดประสงค์เขาคืออยากให้เราเชื่อ ปัญหาจึงอยู่ที่พวกเราต่างหาก ว่าสะสมความรู้ให้เพียงพอกับการรับมือการใช้สื่อ จากคนบางคนได้อย่างมีภูมิคุ้มกันแค่ไหน เพราะเกมส์นี้ก็ยังคงต้องดำเนินต่อไปจนกว่าการครอบครองตลาดจะสมบูรณ์ครับ ดังนั้น information attack ก็ยังคงดำเนินต่อไป ไม่ว่าจะด้านสารอาหาร การรักโลก หรือ สิ่งที่ทำให้หนักใจเสมอ แล้วมีความกดดันอย่างสูงนั่นคือ การลงมาเล่นด้าน จริยธรรม
คำถามที่สำคัญเหนือสิ่งใดคือ ทางรอดคืออะไร
ผมแนบต้นฉบับบทความนั้นมาให้ด้วยครับ ต้องยอมรับครับว่าเขียนได้ดีเลยและน่าคล้อยตามมากๆ อ่อ อ่านแล้วคุ้นๆไหมครับ ที่เฮียเคยเตือนว่า อย่าไปตั้งให้นมเป็นอาหารเทพนัก หลายๆส่วนระหว่างบรรทัด ก็ใช่ว่าจะไม่จริงไปเสียทั้งหมดนะครับ แค่บริบทโดยรวม มัน mislead ไปหน่อย
Lactose, we need to talk: The drama behind dairy’s hidden sugar
Cue the violins—it’s the classic love story with a tragic twist: us and dairy. We crave it, we drizzle it, we melt it, we scoop it. But hidden beneath that creamy, dreamy goodness? A troublemaker called lactose.
It might sound harmless, but for a lot of us, lactose is the culprit behind dairy’s not-so-pleasant side effects. In fact, the majority of the world’s population struggles to digest it properly.
So why do we keep chugging cow’s milk like it’s the elixir of life? And how did dairy become such a staple in our diets?
Grab your favorite cheese alternative (might we suggest Frischhain?) and join us for a deep dive into the world of lactose—what it is, why it matters, and how we are stepping in with our animal-free cheese to save the day.
“In a way, being able to chug a glass of milk without consequences is actually a genetic anomaly—one that we pretty much engineered ourselves over thousands of years.” The inside scoop: What’s LActose? Let’s start with the basics. Lactose is the natural sugar found in dairy milk—a built-in sweetener, if you will. But here’s the twist: your body needs a special enzyme called lactase to break it down. Without enough lactase, lactose turns into the life of the digestion-party you didn’t RSVP to: bloating, cramps, and a whole lot of regret.
As infants, our bodies produce plenty of lactase to digest breast milk. But for most of us, that enzyme naturally switches off once we grow into adulthood. In fact, until just a few thousand years ago, lactose intolerance (or “lactase nonpersistence”) was the norm for all adults.
Lactose Tolerance: A genetic Mutation Still today, nearly 70% of the global population are actually lactose intolerant—so, a heck of a lot of people. In certain regions, like East Asia and Africa, that number shoots up to almost 100%. But then, there’s a select few of us who can drink dairy milk without any drama. How’s that possible?
Well, here’s where it gets interesting. The ability to digest lactose as adults—also known as “lactase persistence”—isn’t evenly spread across the globe. Instead, it’s much more common in certain populations—specifically, those with a long history of dairying. Over 10,000 years ago, some humans began herding cows and drinking their milk, eventually triggering a genetic mutation that allowed them to keep producing lactase into adulthood. This trait is especially common in Northern Europe, for instance in Scandinavia and the Netherlands, where dairy farming has been a way of life for millennia.
It may sound weird, but essentially, some populations forced their own evolution by consuming a whole lot of dairy. That’s right. In a way, being able to chug a glass of milk without consequences is actually a genetic anomaly—one that we pretty much engineered ourselves over thousands of years.
The Dairy dilemma: why drink milk from cows? When you really stop and think about it, the need for this genetic mutation kind of makes sense—because, well, we’re not baby cows.
Just like human breast milk is designed to nourish human babies, cow’s milk is specifically made to take a tiny calf and turn it into a full-grown, 500-kilo cow—fast. It’s packed with nutrients meant to help calves double their birth weight in just a couple of months and pack on hundreds of kilos in their first year.
And yet, here we are, well past weaning age, still reaching for a glass of milk—and not just any milk, but milk from an entirely different species. Yeah… kinda weird, huh?
Wait… Do we even need Dairy milk? Remember those food pyramids we all grew up with—the ones that taught us that milk = calcium = strong bones? Well, here’s the interesting part: while we’ve been led to believe that dairy is the ultimate source of calcium, we can actually absorb up to twice as much calcium from leafy greens like kale and bok choy or from broccoli than from milk. Plus, other plant-based sources like firm tofu, fortified plant milks, and fortified juices have plenty of calcium, too.
And here’s the real kicker: more milk doesn’t always mean stronger bones. In fact, several recent studies suggest that high dairy consumption may actually increase the risk of fractures—especially in women. Who saw that coming?
Oh, and while we were all chugging milk to “build strong bones,” no one mentioned the extra ingredients tagging along—cholesterol, antibiotics, growth hormones… and who knows what else.
Some not-so-lovely side effects Alright, let’s get real for a moment. Dairy isn’t just a digestion bummer for many—it can be linked to serious health risks:
Heart Disease & High Cholesterol: Dairy is loaded with saturated fat, contributing to heart disease, type 2 diabetes, and even Alzheimer’s. Increased Cancer Risk: High dairy intake has been tied to higher risks of liver, breast, ovarian, and prostate cancers. Skin Woes: Acne, eczema, and premature aging can be unwelcome side effects of dairy consumption. Dairy has been marketed as a universal health food for decades, yet its consumption patterns have been shaped more by industry influence than genuine nutritional necessity. Lactose intolerance isn’t a niche issue—it’s a reminder that our dietary norms are far from one-size-fits-all.
Beyond lactose: The ripple effects of dairy But avoiding dairy isn’t just about avoiding an upset stomach—it’s about the planet and the animals, too. Dairy farming uses a staggering amount of water and land, and the industry is a huge contributor to greenhouse gas emissions. Not to mention, billions of cows suffer day in, day out, just so we can drink their milk.
And, while we’re at it, let’s bust a myth real quick. That comforting little story about how somehow, we’re “doing cows a favor” by milking them constantly—because otherwise, they’d explode or something? Well…that’s not exactly how it works. Like humans, cows don’t just produce milk on command. They only lactate after giving birth, and in the dairy industry, that’s usually after forcible artificial insemination. Mother and baby are separated almost immediately, and the male calves? They’re either sent to the veal industry or killed right away as surplus.
Cows aren’t built to be milked non-stop, and the constant milking can cause serious health problems, like mastitis (a painful udder infection), lameness, and other injuries.
So yeah—not exactly the family-friendly scenes you might imagine.
“Our mission goes beyond creating tasty alternatives—we’re envisioning a future where indulgence doesn’t come at the expense of animals or the planet.” The frischhain twist: animal-free, lactose-free, problem-free Let’s face it: traditional dairy has a lot of baggage. But breaking up with lactose doesn’t mean giving up on cheese*alternatives. That’s where we come in.
Our animal-free cheese is crafted without cows, using cutting-edge microfermentation to produce Koji protein—closely resembling traditional whey proteins. The result? Delicious cheese*alternatives that’s better for your tummy, your health, and the planet.
No more bloating. No more stomach aches. Just cheesy*alternative goodness—guilt-free.
What’s more, each pack of our cream cheese alternative Frischhain packs 10.9g of protein, saves 1.2kg of CO2 emissions, and uses far less water and land. If that’s not reason enough to give it a go, we’re not sure what is!
why cutting down on dairy is a win for everyone Look, even if you’re not lactose intolerant, switching to animal-free dairy has major perks:
Happy Digestion: Dairy-free options make digestion smoother and help prevent bloating, discomfort, and even energy crashes. Better Skin & Hormones: Going dairy-free can improve skin clarity, reduce inflammation, and balance hormones. Planet-Friendly: Ditching dairy helps reduce excessive water use, land destruction, and greenhouse gas emissions. It’s an easy way to reduce your carbon footprint. Cruelty-Free: Supporting dairy alternatives means less harm to animals, especially the billions of cows in factory farms the future of dairy: diverse, delicious, and dairy-free One of the most exciting aspects of shifting away from traditional dairy is the sheer diversity of alternatives. From fermented nut cheeses to innovative proteins made with micro fermentation, the industry is moving beyond simple substitutions and into entirely new taste and texture experiences. Lactose-free options have never been more delicious or more readily available. And the best part? They’re made for humans, not cows.
Our mission goes beyond creating tasty alternatives—we’re envisioning a future where indulgence doesn’t come at the expense of animals or the planet. So, whether you’re lactose-intolerant, eco-conscious, or just obsessed with really good cheesealternatives, why not give our cow-free cheesealternative a try? The future of dairy is here—and it’s deliciously dairy-free.
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 0fa80bd3:ea7325de
2025-04-09 21:19:39
@ 0fa80bd3:ea7325de
2025-04-09 21:19:39DAOs promised decentralization. They offered a system where every member could influence a project's direction, where money and power were transparently distributed, and decisions were made through voting. All of it recorded immutably on the blockchain, free from middlemen.
But something didn’t work out. In practice, most DAOs haven’t evolved into living, self-organizing organisms. They became something else: clubs where participation is unevenly distributed. Leaders remained - only now without formal titles. They hold influence through control over communications, task framing, and community dynamics. Centralization still exists, just wrapped in a new package.
But there's a second, less obvious problem. Crowds can’t create strategy. In DAOs, people vote for what "feels right to the majority." But strategy isn’t about what feels good - it’s about what’s necessary. Difficult, unpopular, yet forward-looking decisions often fail when put to a vote. A founder’s vision is a risk. But in healthy teams, it’s that risk that drives progress. In DAOs, risk is almost always diluted until it becomes something safe and vague.
Instead of empowering leaders, DAOs often neutralize them. This is why many DAOs resemble consensus machines. Everyone talks, debates, and participates, but very little actually gets done. One person says, “Let’s jump,” and five others respond, “Let’s discuss that first.” This dynamic might work for open forums, but not for action.
Decentralization works when there’s trust and delegation, not just voting. Until DAOs develop effective systems for assigning roles, taking ownership, and acting with flexibility, they will keep losing ground to old-fashioned startups led by charismatic founders with a clear vision.
We’ve seen this in many real-world cases. Take MakerDAO, one of the most mature and technically sophisticated DAOs. Its governance token (MKR) holders vote on everything from interest rates to protocol upgrades. While this has allowed for transparency and community involvement, the process is often slow and bureaucratic. Complex proposals stall. Strategic pivots become hard to implement. And in 2023, a controversial proposal to allocate billions to real-world assets passed only narrowly, after months of infighting - highlighting how vision and execution can get stuck in the mud of distributed governance.
On the other hand, Uniswap DAO, responsible for the largest decentralized exchange, raised governance participation only after launching a delegation system where token holders could choose trusted representatives. Still, much of the activity is limited to a small group of active contributors. The vast majority of token holders remain passive. This raises the question: is it really community-led, or just a formalized power structure with lower transparency?
Then there’s ConstitutionDAO, an experiment that went viral. It raised over $40 million in days to try and buy a copy of the U.S. Constitution. But despite the hype, the DAO failed to win the auction. Afterwards, it struggled with refund logistics, communication breakdowns, and confusion over governance. It was a perfect example of collective enthusiasm without infrastructure or planning - proof that a DAO can raise capital fast but still lack cohesion.
Not all efforts have failed. Projects like Gitcoin DAO have made progress by incentivizing small, individual contributions. Their quadratic funding mechanism rewards projects based on the number of contributors, not just the size of donations, helping to elevate grassroots initiatives. But even here, long-term strategy often falls back on a core group of organizers rather than broad community consensus.
The pattern is clear: when the stakes are low or the tasks are modular, DAOs can coordinate well. But when bold moves are needed—when someone has to take responsibility and act under uncertainty DAOs often freeze. In the name of consensus, they lose momentum.
That’s why the organization of the future can’t rely purely on decentralization. It must encourage individual initiative and the ability to take calculated risks. People need to see their contribution not just as a vote, but as a role with clear actions and expected outcomes. When the situation demands, they should be empowered to act first and present the results to the community afterwards allowing for both autonomy and accountability. That’s not a flaw in the system. It’s how real progress happens.
-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ 21335073:a244b1ad
2025-03-18 14:43:08
@ 21335073:a244b1ad
2025-03-18 14:43:08Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ f85b9c2c:d190bcff
2025-05-14 23:41:47
@ f85b9c2c:d190bcff
2025-05-14 23:41:47My secret to making money while the market is crashing.
 .
.Hey there! I’m just an average person who stumbled into the wild world of cryptocurrency a few years back. Like most people, I’ve seen the ups and downs—those euphoric highs when Bitcoin hits a new all-time high and the gut-wrenching lows when the market crashes and everyone panics. But here’s the thing: I’ve figured out a way to make money even when the charts are bleeding red. Today, I’m spilling my secret on how I turn crypto crashes into cash. Let's dive in!
Why Market Crashes Don’t Scare Me Anymore. When I first started in crypto, a market crash would send me into a spiral. I’d watch my portfolio shrink and feel like I’d made a huge mistake. But over time, I realized something: crashes are just part of the game. They’re not the end—they’re an opportunity. The trick is shifting your mindset. Instead of seeing a crash as a loss, I now see it as a sale. Prices drop, panic sets in, and that’s when I get to work. Here’s how I do it.
Here’s my secret technique. 1.Buying the Dip: My Go-To Move: You’ve probably heard the phrase “buy low, sell high.” It sounds simple, but it’s my bread and butter during a crash. When the market tanks, I don’t run away—I lean in. I keep some cash (or stablecoins like USDT) ready on the sidelines for these moments. When I see a solid project—like Ethereum, Solana, or even some smaller altcoins I’ve researched—drop 30%, 50%, or more, I scoop it up. For example, during the last big crash, I grabbed some ETH at a price I hadn’t seen in months. A few weeks later, when the market bounced back, I sold a chunk of it for a tidy profit. The key? Patience and knowing what I’m buying. I don’t just throw money at random coins—I stick to projects with strong fundamentals that I believe will recover.
2.Staking: Earning While I Wait: Here’s where my secret really shines: staking. When the market crashes, I don’t just sit on my coins and hope for the best. I put them to work. Staking is like earning interest on your crypto—you lock it up in a wallet or platform, and you get rewarded with more coins over time. During a downturn, I stake coins like Cardano (ADA) or Polkadot (DOT) on platforms I trust. The beauty is, even if the price is low, I’m still earning extra tokens. By the time the market recovers, I’ve got more coins than I started with, plus the price is climbing. It’s like getting paid to wait out the storm. Last crash, ascended to the top of the food chain, and I’m loving it.
3.Selling High: Timing Is Everything: Buying low is only half the equation—I also know when to sell. I don’t get greedy. When a coin I’ve staked or bought cheap starts pumping after a crash, I take profits. I don’t wait for the “moon” because I’ve learned the hard way that crypto can turn on a dime. My rule? If I’ve doubled my money or hit a target I set, I sell a portion and keep the rest for the long haul. It’s a balance—cash in some gains but stay in the game.
My Secret Sauce: Staying Calm: The real secret isn’t just the strategies—it’s me. I don’t panic. I don’t FOMO into hype. I stick to my plan, do my homework, and tune out the noise. Crypto is emotional, but I’ve trained myself to think long-term. Crashes don’t last forever, and I’ve seen enough cycles to know the market always bounces back. That’s how I make money while everyone else is losing their minds.
My Final Thoughts Making money in crypto during a crash isn’t magic—it’s about preparation, patience, and playing smart. I buy when others sell, stake to grow my stash, and sell when the time’s right. It’s worked for me, and I’m still learning every day. So next time the market crashes, don’t freak out—see it as your chance to cash in.
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 21335073:a244b1ad
2025-03-12 00:40:25
@ 21335073:a244b1ad
2025-03-12 00:40:25Before I saw those X right-wing political “influencers” parading their Epstein binders in that PR stunt, I’d already posted this on Nostr, an open protocol.
“Today, the world’s attention will likely fixate on Epstein, governmental failures in addressing horrific abuse cases, and the influential figures who perpetrate such acts—yet few will center the victims and survivors in the conversation. The survivors of Epstein went to law enforcement and very little happened. The survivors tried to speak to the corporate press and the corporate press knowingly covered for him. In situations like these social media can serve as one of the only ways for a survivor’s voice to be heard.
It’s becoming increasingly evident that the line between centralized corporate social media and the state is razor-thin, if it exists at all. Time and again, the state shields powerful abusers when it’s politically expedient to do so. In this climate, a survivor attempting to expose someone like Epstein on a corporate tech platform faces an uphill battle—there’s no assurance their voice would even break through. Their story wouldn’t truly belong to them; it’d be at the mercy of the platform, subject to deletion at a whim. Nostr, though, offers a lifeline—a censorship-resistant space where survivors can share their truths, no matter how untouchable the abuser might seem. A survivor could remain anonymous here if they took enough steps.
Nostr holds real promise for amplifying survivor voices. And if you’re here daily, tossing out memes, take heart: you’re helping build a foundation for those who desperately need to be heard.“
That post is untouchable—no CEO, company, employee, or government can delete it. Even if I wanted to, I couldn’t take it down myself. The post will outlive me on the protocol.
The cozy alliance between the state and corporate social media hit me hard during that right-wing X “influencer” PR stunt. Elon owns X. Elon’s a special government employee. X pays those influencers to post. We don’t know who else pays them to post. Those influencers are spurred on by both the government and X to manage the Epstein case narrative. It wasn’t survivors standing there, grinning for photos—it was paid influencers, gatekeepers orchestrating yet another chance to re-exploit the already exploited.
The bond between the state and corporate social media is tight. If the other Epsteins out there are ever to be unmasked, I wouldn’t bet on a survivor’s story staying safe with a corporate tech platform, the government, any social media influencer, or mainstream journalist. Right now, only a protocol can hand survivors the power to truly own their narrative.
I don’t have anything against Elon—I’ve actually been a big supporter. I’m just stating it as I see it. X isn’t censorship resistant and they have an algorithm that they choose not the user. Corporate tech platforms like X can be a better fit for some survivors. X has safety tools and content moderation, making it a solid option for certain individuals. Grok can be a big help for survivors looking for resources or support! As a survivor, you know what works best for you, and safety should always come first—keep that front and center.
That said, a protocol is a game-changer for cases where the powerful are likely to censor. During China's # MeToo movement, survivors faced heavy censorship on social media platforms like Weibo and WeChat, where posts about sexual harassment were quickly removed, and hashtags like # MeToo or "woyeshi" were blocked by government and platform filters. To bypass this, activists turned to blockchain technology encoding their stories—like Yue Xin’s open letter about a Peking University case—into transaction metadata. This made the information tamper-proof and publicly accessible, resisting censorship since blockchain data can’t be easily altered or deleted.
I posted this on X 2/28/25. I wanted to try my first long post on a nostr client. The Epstein cover up is ongoing so it’s still relevant, unfortunately.
If you are a survivor or loved one who is reading this and needs support please reach out to: National Sexual Assault Hotline 24/7 https://rainn.org/
Hours: Available 24 hours
-
 @ 04c915da:3dfbecc9
2025-03-10 23:31:30
@ 04c915da:3dfbecc9
2025-03-10 23:31:30Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Usually stolen bitcoin for the reserve creates a perverse incentive. If governments see a bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 67e9dd72:b9d59ce7
2025-05-14 20:59:36
@ 67e9dd72:b9d59ce7
2025-05-14 20:59:36There’s a certain elegance to outliving your enemies. Not the cinematic kind, with poisoned cigars or cunning plots, but the quieter, more refined triumph of still being around when everyone who ever underestimated you has long since retired, expired, or become inexplicably fond of sudoku. It’s a victory without confetti. You simply keep showing up, well-dressed and unimpressed.

Bob Hope may not be a household name anymore, but for much of the 20th century, he was practically a part of everyone’s household. Born in 1903, he became the blueprint for the modern entertainer: part comedian, part actor, part relentless emcee of the American psyche.
Man - Bob Hope - in a checkered suit and striped tie smiles in a black and white photo. Blurred foliage in the background.
Before stand-up was a career path and before anyone thought to put jokes on late-night television, Hope was crisscrossing the globe with a microphone in one hand and a golf club in the other, cracking wise for movie stars, eleven presidents, and countless thousands of homesick soldiers. He wasn’t just famous - he was a part of the family. Your grandparents didn’t need to like comedy to know who Bob Hope was. He was baked into the cultural cake.
But what makes him worthy of this list isn’t just his longevity - though making it to 100 with your timing intact is no small feat. It’s that he stayed Bob Hope the whole time. He managed to remain a household name through every major technological shift from vaudeville to cable. Always with the same self-deprecating grin, the same deadpan delivery, the same tireless drive to entertain, whether on a dusty military base, golf club in hand, or a glitzy awards stage.
A man on stage - Bob Hope - in front of a large crowd of soldiers, some holding "BOB" signs. The mood is lively, with soldiers clapping and smiling.
In a business that burns through personalities like kindling, Hope managed to stay relevant without ever pretending to be something he wasn’t. He adapted, yes - but he never shape-shifted. And that’s no punchline; that’s staying power.
David Attenborough (Honorable Mention 1926 - )
Sir David Attenborough hasn’t just lived for nearly a century - he’s narrated it.
Elderly man in a blue suit - David Attenborough - smiles softly outdoors with blurred green background. He has white hair and wears a white shirt, conveying warmth.
Born in 1926, he’s now pushing the hundred mark with the same quiet intensity and clipped eloquence that made "Planet Earth" a phrase we all say with reverence. For decades, Attenborough has been the voice in our heads while we watch iguanas outrun snakes or bioluminescent squid flash their Morse code in the abyss. But beyond the velvet tones and impeccable suits, there’s something more enduring: a man who has remained unflinchingly curious in a world that increasingly isn’t. While others have shouted into the void, Attenborough has whispered, and when he whispers, we listened.
What makes him extraordinary isn’t just the longevity - it’s the fact that he’s never softened his message to suit the moment. In his nineties, when most people are congratulated for remembering their Wi-Fi password, Attenborough was delivering urgent speeches at climate summits and lending gravitas to a collapsing ecosystem. He has aged, yes, but never aged out. His moral clarity, his scientific reverence, and his profound respect for the natural world have never been dulled by time. If anything, they've sharpened.
Elderly man - David Attenborough - seated on a wooden chair with arms crossed, wearing a gray sweater against a dark background. Calm, contemplative expression.
Sir David may be approaching 100, but he's still out there - gently scolding us, brilliantly informing us, and above all, remaining unmistakably, irreplaceably himself.
Fauja Singh (1911 - )
Fauja Singh didn’t just reach 100 - he ran there.
Elderly man - Fauja Singh - jogging on a grassy hill, wearing a yellow turban and sportswear. City skyline and lush greenery in the background. Calm mood.
Born in 1911 in British India, he took up competitive marathon running in his 80s, which is roughly the age most people start describing trips to the mailbox as “exercise.” At 100, he completed the Toronto Waterfront Marathon, becoming the first centenarian to do so. He wasn’t running for medals or money or anyone’s approval - he was running because his legs still said yes. In a culture obsessed with youth and speed, Singh offered something quietly radical: the image of an old man moving forward, steadily, joyfully, and entirely on his own terms.
But what truly sets Fauja Singh apart isn't just the records - though those are impressive - but the gentleness with which he carried them. Soft-spoken, devoutly Sikh, and famously modest, he turned down sponsorships that conflicted with his values and credited his endurance to simple living and a vegetarian diet. No drama, no bravado - just resolve in motion.
Elderly man - Fauja Singh - with a long beard and dark turban smiling, outdoors near a track field. Background shows trees and houses, soft sunset lighting.
While the world sprinted around him in search of the next thing, Singh – who is still with us at 114 - kept his pace and kept his faith. He didn’t just defy age - he ignored it. And in doing so, he reminds us that time is less an enemy to be conquered than a companion to be outwalked, one calm mile at a time.
Henry Allingham (1896 – 2009)
Henry Allingham lived to be 113, which is remarkable enough - but what makes him truly unforgettable is how he carried those years. Born in 1896, he lived through both World Wars, the sinking of the Titanic, the moon landing, and the invention of sliced bread - literally. A founding member of the Royal Air Force and one of the last surviving veterans of World War I, Allingham wasn’t just a man from another time; he was a walking archive of it.
Elderly man - Henry Allingham - smiling with a certificate showing military service details, birth and death dates, and text "The last founding member of the Royal Air Force."
When asked about the secret to his longevity, he famously answered: "Cigarettes, whisky, and wild women." Which may not hold up in a medical journal, but certainly qualifies as staying defiantly oneself.
But beneath the cheeky quotes was someone deeply committed to remembrance. In his later years, Allingham didn’t retreat into private comfort - he leaned in. He spent his 100’s traveling, speaking, and bearing witness for those who no longer could. He wore his medals not as decorations, but as responsibilities. There was something dignified yet unsentimental in the way he spoke about war and peace, as if to say: this happened, and it mattered, and I’m still here to make sure you understand that.
Elderly man - Henry Allingham - saluting, wearing a suit, striped tie, and several medals. Background blurred. Solemn expression.
Henry Allingham didn’t just endure time - he honored it, and in doing so, made his century count for more than just numbers.
George Burns (1896 – 1996)
George Burns made it to 100 with a cigar in one hand and a punchline in the other, which is more or less how he lived every year of his life.
Elderly man - comedian George Burns - with glasses in plaid jacket holds cigar, raising hand with a playful expression against a gray background.
Born in 1896, he started in vaudeville, graduated to radio, then television, and eventually film - playing God, no less, in his later years, with the same dry charm he used to dismantle hecklers back in the 1920s. He didn’t just age into comedy; he dragged comedy along with him, evolving without ever losing that sly, arched-eyebrow delivery that made it all look effortless. Burns didn’t just outlast his peers - he made a habit of burying them with style, then cracking a joke at the funeral.
What made Burns so enduring wasn’t just the longevity or the accolades (though he won an Oscar at 80 and was still headlining Vegas in his 90’s). It was the unshakable sense of self. He never rebranded or reimagined - he refined.
Elderly man - comedian George Burns - in a tuxedo holds a lit cigar, standing at a microphone on a dark stage. Smoky atmosphere, calm demeanor.
While the world swirled around him in reinvention and reinvention’s younger cousin, desperation, George Burns stayed exactly who he was: a little irreverent, a little sentimental, and always in on the joke. When he turned 100, it didn’t feel like a milestone - it felt like the final beat in a perfectly timed routine.
Irving Berlin (1888 – 1989)
Irving Berlin didn’t just live to 101 - he scored most of the 20th century along the way. Born in 1888 in Imperial Russia and arriving in the U.S. as a penniless immigrant, he wrote more than 1,500 songs, including “White Christmas,” “God Bless America,” and “There’s No Business Like Show Business”.
Man in a suit - Irving Berlin - sits in front of a piano, with sheet music behind him. He appears poised and relaxed in a monochromatic setting.
His melodies are so deeply embedded in American culture that they feel almost like public domain, like oxygen, or like awkward family holidays. Yet Berlin never read music and played only in F-sharp, the black keys. He succeeded by sheer force of will, instinct, and an uncanny ability to write songs that people didn’t just want to hum - they wanted to live inside.
What makes him truly worthy of this list, though, isn’t just his prodigious output or his improbable rise. It’s that even into his centenarian years, Berlin never stopped being Berlin.
Elderly man in suit - Irving Berlin - plays piano in a dimly lit room, glancing at the camera. Books and a framed picture are seen in the background.
He remained fiercely private, unassuming, and somewhat allergic to praise. He turned down presidential medals and refused to attend tribute concerts in his honor. He didn’t care for celebrity; he cared for the work. And when the applause faded, he kept playing - quietly, defiantly, on his beloved black keys. In a century that was loud, fast, and eager to reinvent itself, Irving Berlin stood still and let the world dance to his tune.
Shigeaki Hinohara (1911 - 2017)
Shigeaki Hinohara lived to the age of 105, and if that alone doesn’t impress you, consider this: he spent most of that time working.
Elderly person wearing glasses and a white coat - Shigeaki Hinohara - with a stethoscope, smiling warmly. Indoors with wooden background, calm and professional mood.
As one of Japan’s most beloved physicians and a pioneer of preventive medicine, he wrote more than 150 books (some of them after turning 100), saw patients well into his centenarian years, and advocated tirelessly for a lifestyle of purpose, moderation, and fun. He was known to skip lunch, take the stairs, and insist that people shouldn’t retire just because a calendar told them to. In a culture that reveres longevity but often equates age with retreat, Hinohara cheerfully subverted the narrative - by refusing to slow down.
What made Hinohara truly remarkable was not just how long he lived, but how completely he inhabited his philosophy. He believed that life should be driven by curiosity, not calories, by engagement, not age. He didn’t just dish out wellness advice - he embodied it, always immaculately dressed, sharp-witted, and quietly radical in his refusal to become ornamental.
Elderly man in a brown suit - Shigeaki Hinohara - sits on a stone bench with arms raised, smiling in a grassy park. Plaque visible on the bench.
Even as the world around him grew faster, flashier, more disposable, Hinohara stayed grounded in old-school service and a kind of optimistic realism that’s now in short supply. He lived the life of a man who had somewhere to be and something to say, right up to the very end. And he never once apologized for being himself.
Ernst Mayr (1904 – 2004)
Ernst Mayr lived to be 100 and managed to spend nearly all of it arguing - politely, rigorously, and with great precision - about the nature of life itself. Born in 1904 in what was then the German Empire, Mayr became one of the most influential evolutionary biologists of the 20th century, helping to unify Darwinian theory with modern genetics in what became known as the “modern synthesis.”
Black-and-white image of an elderly man in a suit, smiling against a dark background. Text: "NCERT Biology, Ernst Mayr, Darwin of the 20th century."
He wrote or co-authored more than 20 books, described dozens of new species, and spent his final years calmly but insistently reminding the scientific community that speciation was, in fact, his specialty. To say he had staying power is an understatement; the man didn’t just contribute to biology - he helped rewrite its central grammar, and then stuck around to make sure no one messed it up. Darwin certainly would’ve been nodding in approval
What makes Mayr a qualified member of this centenarian pantheon isn’t just the duration of his life, but the clarity of his voice within it. Even into his late 90s, he was publishing papers, giving interviews, and confidently dismantling sloppy evolutionary thinking wherever he found it.
Man - Ernst Mayr - smiling beside a portrait of himself in academic robes. Black-and-white setting with framed document visible in background.
He was precise without being precious, critical without being cruel, and never once dulled his intellectual edge for the sake of being agreeable. If anything, he seemed to sharpen with age, like a scalpel left in a glass case: elegant, useful, and just a bit intimidating. Mayr didn’t merely witness a century of science - he shaped it, defended it, and remained unmistakably himself every step of the way.
Ernest Badalian (1925 - )
Born in Armenia during the early days of the Soviet experiment, Ernie Badalian came into a world already complicated, already tilting on its axis.
Elderly man - Ernie Badalian - smiling warmly, wearing a blue patterned shirt, and waving. Seated on a patterned chair in a well-lit room.
His father was a landowner – code word at the time, for “enemy of the people” - and the family’s property was seized by Soviet authorities in a sweeping purge of the bourgeoisie. To avoid a one-way ticket to the gulag, the family fled. They moved west through Europe’s unraveling seams, only to find themselves caught in the gears of World War II. Ernie was eventually interned in a German POW camp, where he remained until American forces liberated it in 1945. Freedom came not with fanfare, but with the quiet, improbable survival of someone who simply refused to be broken.
From there, Ernie’s story veers not into comfort, but resilience reimagined. He made it to America. He reunited with family - every last one of them, which in itself feels almost mythic – in Detroit, Michigan and became an American citizen. In 1952, he landed in Bell, California, bought a poultry ranch, and then - in one of those only-in-America plot twists - pivoted from chickens to check-ins by opening a motel across the street from a brand-new curiosity called Disneyland. That little venture became a family business, a generational stake in the American dream, and at 100, Ernie still lives on-site, quietly keeping tabs on tourists and trendlines like a man who knows full well the cost of standing still.
What makes Ernie a charter member of this list isn’t just that he reached the far end of the calendar with his humor and will intact - it’s that he did so by shaping every chapter himself. His life is a testament to persistence without self-pity, adaptation without loss of identity, and the kind of quiet authority that doesn’t need reminding who’s in charge. That he was the inspiration for this post is no coincidence. He’s not just a part of the list - he’s the reason it exists.
Older man - Ernie Badalian - sits with "100" birthday balloon, smiling, in a restaurant. Another man - Chris Zappia - stands behind him, also smiling. Warm, lively atmosphere.
Maybe the best thing about the people on this list - besides the obvious fact that they absolutely refuse to die on anyone else's schedule - is that they never mistook longevity for the goal. They weren’t chasing years like some kind of loyalty program. They were just busy living. Fully. Messily. With style, principle, or just stubbornness, but always on their own terms. Making it to 100 is impressive. Making it to 100 without becoming a museum exhibit or a punchline? That’s something else entirely.
It’s tempting to reduce centenarians to life hacks and headlines. “Secrets to a Long Life Revealed!” followed by kale, crossword puzzles, and something vaguely Scandinavian. But the truth is more slippery and less clickable. These people didn’t age gracefully - they aged honestly. There’s a difference. They didn’t live long because they tried to. They lived long because they kept moving, kept showing up, kept refusing to trade curiosity for comfort. Some ran marathons. Some played God. Some just kept opening their motel door every morning, because, to them, the world was still worth checking in on.
There’s no single through-line in this list - no magic pill, no secret sauce, no TED Talk formula. Just people who stayed sharp, stayed weird, or stayed kind long enough to watch the rest of us try to catch up. They kept going. Not because it was easy, but because it never occurred to them to stop. And when the rest of the world started putting up walls - between generations, between truths, between each other - they walked through them like smoke. And maybe that’s the real lesson here. Not how to live forever, but how to live so well, so completely, that the calendar just becomes background noise. The trick, it seems, isn’t to avoid the end. It’s to make the middle matter so much that the end doesn’t get the last word.
So, raise a glass (neat, no ice!) to the centenarians - the defiant, the dignified, the quietly miraculous. Not because they beat the clock, but because they never let it run the show. They remind us, in their beautifully stubborn way, that time is less a thief than a mirror. It reflects what you put into it. And if you’re lucky - and just a little bit ungovernable - it reflects you right back, 100 years later, with a raised eyebrow and a drink in hand.
-
 @ 4925ea33:025410d8
2025-03-08 00:38:48
@ 4925ea33:025410d8
2025-03-08 00:38:481. O que é um Aromaterapeuta?

O aromaterapeuta é um profissional especializado na prática da Aromaterapia, responsável pelo uso adequado de óleos essenciais, ervas aromáticas, águas florais e destilados herbais para fins terapêuticos.
A atuação desse profissional envolve diferentes métodos de aplicação, como inalação, uso tópico, sempre considerando a segurança e a necessidade individual do cliente. A Aromaterapia pode auxiliar na redução do estresse, alívio de dores crônicas, relaxamento muscular e melhora da respiração, entre outros benefícios.
Além disso, os aromaterapeutas podem trabalhar em conjunto com outros profissionais da saúde para oferecer um tratamento complementar em diversas condições. Como já mencionado no artigo sobre "Como evitar processos alérgicos na prática da Aromaterapia", é essencial ter acompanhamento profissional, pois os óleos essenciais são altamente concentrados e podem causar reações adversas se utilizados de forma inadequada.
2. Como um Aromaterapeuta Pode Ajudar?

Você pode procurar um aromaterapeuta para diferentes necessidades, como:
✔ Questões Emocionais e Psicológicas
Auxílio em momentos de luto, divórcio, demissão ou outras situações desafiadoras.
Apoio na redução do estresse, ansiedade e insônia.
Vale lembrar que, em casos de transtornos psiquiátricos, a Aromaterapia deve ser usada como terapia complementar, associada ao tratamento médico.
✔ Questões Físicas
Dores musculares e articulares.
Problemas respiratórios como rinite, sinusite e tosse.
Distúrbios digestivos leves.
Dores de cabeça e enxaquecas. Nesses casos, a Aromaterapia pode ser um suporte, mas não substitui a medicina tradicional para identificar a origem dos sintomas.
✔ Saúde da Pele e Cabelos
Tratamento para acne, dermatites e psoríase.
Cuidados com o envelhecimento precoce da pele.
Redução da queda de cabelo e controle da oleosidade do couro cabeludo.
✔ Bem-estar e Qualidade de Vida
Melhora da concentração e foco, aumentando a produtividade.
Estímulo da disposição e energia.
Auxílio no equilíbrio hormonal (TPM, menopausa, desequilíbrios hormonais).
Com base nessas necessidades, o aromaterapeuta irá indicar o melhor tratamento, calculando doses, sinergias (combinação de óleos essenciais), diluições e técnicas de aplicação, como inalação, uso tópico ou difusão.
3. Como Funciona uma Consulta com um Aromaterapeuta?

Uma consulta com um aromaterapeuta é um atendimento personalizado, onde são avaliadas as necessidades do cliente para a criação de um protocolo adequado. O processo geralmente segue estas etapas:
✔ Anamnese (Entrevista Inicial)
Perguntas sobre saúde física, emocional e estilo de vida.
Levantamento de sintomas, histórico médico e possíveis alergias.
Definição dos objetivos da terapia (alívio do estresse, melhora do sono, dores musculares etc.).
✔ Escolha dos Óleos Essenciais
Seleção dos óleos mais indicados para o caso.
Consideração das propriedades terapêuticas, contraindicações e combinações seguras.
✔ Definição do Método de Uso
O profissional indicará a melhor forma de aplicação, que pode ser:
Inalação: difusores, colares aromáticos, vaporização.
Uso tópico: massagens, óleos corporais, compressas.
Banhos aromáticos e escalda-pés. Todas as diluições serão ajustadas de acordo com a segurança e a necessidade individual do cliente.
✔ Plano de Acompanhamento
Instruções detalhadas sobre o uso correto dos óleos essenciais.
Orientação sobre frequência e duração do tratamento.
Possibilidade de retorno para ajustes no protocolo.
A consulta pode ser realizada presencialmente ou online, dependendo do profissional.
Quer saber como a Aromaterapia pode te ajudar? Agende uma consulta comigo e descubra os benefícios dos óleos essenciais para o seu bem-estar!
-
 @ 04c915da:3dfbecc9
2025-03-13 19:39:28
@ 04c915da:3dfbecc9
2025-03-13 19:39:28In much of the world, it is incredibly difficult to access U.S. dollars. Local currencies are often poorly managed and riddled with corruption. Billions of people demand a more reliable alternative. While the dollar has its own issues of corruption and mismanagement, it is widely regarded as superior to the fiat currencies it competes with globally. As a result, Tether has found massive success providing low cost, low friction access to dollars. Tether claims 400 million total users, is on track to add 200 million more this year, processes 8.1 million transactions daily, and facilitates $29 billion in daily transfers. Furthermore, their estimates suggest nearly 40% of users rely on it as a savings tool rather than just a transactional currency.
Tether’s rise has made the company a financial juggernaut. Last year alone, Tether raked in over $13 billion in profit, with a lean team of less than 100 employees. Their business model is elegantly simple: hold U.S. Treasuries and collect the interest. With over $113 billion in Treasuries, Tether has turned a straightforward concept into a profit machine.
Tether’s success has resulted in many competitors eager to claim a piece of the pie. This has triggered a massive venture capital grift cycle in USD tokens, with countless projects vying to dethrone Tether. Due to Tether’s entrenched network effect, these challengers face an uphill battle with little realistic chance of success. Most educated participants in the space likely recognize this reality but seem content to perpetuate the grift, hoping to cash out by dumping their equity positions on unsuspecting buyers before they realize the reality of the situation.
Historically, Tether’s greatest vulnerability has been U.S. government intervention. For over a decade, the company operated offshore with few allies in the U.S. establishment, making it a major target for regulatory action. That dynamic has shifted recently and Tether has seized the opportunity. By actively courting U.S. government support, Tether has fortified their position. This strategic move will likely cement their status as the dominant USD token for years to come.
While undeniably a great tool for the millions of users that rely on it, Tether is not without flaws. As a centralized, trusted third party, it holds the power to freeze or seize funds at its discretion. Corporate mismanagement or deliberate malpractice could also lead to massive losses at scale. In their goal of mitigating regulatory risk, Tether has deepened ties with law enforcement, mirroring some of the concerns of potential central bank digital currencies. In practice, Tether operates as a corporate CBDC alternative, collaborating with authorities to surveil and seize funds. The company proudly touts partnerships with leading surveillance firms and its own data reveals cooperation in over 1,000 law enforcement cases, with more than $2.5 billion in funds frozen.
The global demand for Tether is undeniable and the company’s profitability reflects its unrivaled success. Tether is owned and operated by bitcoiners and will likely continue to push forward strategic goals that help the movement as a whole. Recent efforts to mitigate the threat of U.S. government enforcement will likely solidify their network effect and stifle meaningful adoption of rival USD tokens or CBDCs. Yet, for all their achievements, Tether is simply a worse form of money than bitcoin. Tether requires trust in a centralized entity, while bitcoin can be saved or spent without permission. Furthermore, Tether is tied to the value of the US Dollar which is designed to lose purchasing power over time, while bitcoin, as a truly scarce asset, is designed to increase in purchasing power with adoption. As people awaken to the risks of Tether’s control, and the benefits bitcoin provides, bitcoin adoption will likely surpass it.
-
 @ 04c915da:3dfbecc9
2025-03-07 00:26:37
@ 04c915da:3dfbecc9
2025-03-07 00:26:37There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ 3b62c542:6f45deaf
2025-05-14 16:09:39
@ 3b62c542:6f45deaf
2025-05-14 16:09:39A New Chapter in Decentralized Finance.
In the ever-evolving world of crypto, the next major disruptor may not come from Silicon Valley or a Fortune 500 boardroom but from the digital grassroots of a movement determined to redefine finance. World Liberty Financial (WLFI), an ambitious decentralized finance (DeFi) project, is staking its claim as the next game changer in blockchain-based financial ecosystems.
With a bold vision of democratizing finance and a token model unlike any other, WLFI may very well be on the verge of something historic.
The Genesis of WLFI;A Mission Beyond Profit.
At its core, World Liberty Financial seeks to upend the long-standing dominance of centralized institutions. Its mission is clear; to empower individuals with direct access to decentralized financial services**, eliminating the need for banks, intermediaries, and regulatory chokeholds.
Leveraging blockchain technology, WLFI aims to provide borderless, transparent, and censorship-resistant alternatives to traditional finance, a concept that resonates strongly in an era of growing distrust toward centralized entities.
The Token Sale;A Rocky Start Turned Power Move.
WLFI’s token sale launched quietly in October 2024, pricing tokens at just \$0.015 with a goal of raising \$1.5 billion. Initial investor sentiment, however, was tepid—only 4% of the 20 billion token supply sold in the early weeks. But as political tides shifted in the U.S. following the 2024 Presidential Election and a more pro-crypto administration came to power, the wind began to change.
A major turning point came with a \$30 million investment from blockchain heavyweight Justin Sun, a move that revitalized confidence and placed WLFI squarely on the radar of institutional and retail investors alike.
By March 2025, WLFI had raised approximately \$590 million, making it one of the largest DeFi token sales in history. While it didn’t reach its lofty initial goal, it proved there was strong market appetite for a platform with real utility and an ambitious roadmap.
Tokenomics: A Bold, Unorthodox Approach.
What truly sets WLFI apart is not just its vision but its controversial and deliberate design choices:
●Non-Transferable Tokens-WLFI tokens currently cannot be traded, sold, or transferred. This is an intentional mechanism to curb speculation and shift focus to governance and utility. That said, community discussions are surfacing around a clause in the smart contract that could eventually allow limited transfers—pending a vote by token holders.
●No Economic Rights—Yet; WLFI tokens carry no economic rights, meaning holders don’t receive profits or dividends by default. However, a future protocol vote may change that, paving the way for dividends in stablecoins or airdrops, making it potentially the first DeFi token with structured financial payouts.
●Equal Governance Power- Every token holder has a seat at the table. Governance proposals and protocol upgrades are voted on democratically, creating a truly decentralized ecosystem where users—not venture capitalists or early insiders—steer the ship.
Tech Stack: Launching with Aave V3 Integration
WLFI’s integration with Aave V3 is a strategic move that immediately places it within a battle-tested DeFi framework. This partnership allows WLFI to:
- Create a decentralized lending and borrowing market
- Share protocol revenues with the Aave DAO
- Leverage Aave’s liquidity infrastructure while maintaining community autonomy
This integration puts WLFI in a unique position to blend the best of existing DeFi innovation with its own ideological twist on community-led finance.
The Bigger Picture: A Rare Window of Opportunity? As the world watches the regulatory and political landscape shift, particularly with a pro-crypto U.S. President in office, WLFI’s timing feels almost poetic. The conditions echo the early days of Bitcoin—uncertain, volatile, and full of opportunity.
But unlike Bitcoin, WLFI offers governance participation, future revenue sharing, and a tangible roadmap. It’s not just a store of value—it’s a financial instrument for the digital age.
Final Thoughts: Hype or Historic? WLFI is not for the impatient or the purely profit-driven investor. It’s a long-game play for those who believe in the foundational principles of decentralization, community governance, and financial sovereignty.
If it delivers on its promises—and if governance votes align to unlock its full potential—World Liberty Financial could be remembered as the moment DeFi stopped being just a tech experiment and started becoming a real financial revolution.
Disclaimer: This article is not financial advice. Always do your own research before investing.
-
 @ 04c915da:3dfbecc9
2025-03-04 17:00:18
@ 04c915da:3dfbecc9
2025-03-04 17:00:18This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ 4cebd4f5:0ac3ed15
2025-05-14 15:06:02
@ 4cebd4f5:0ac3ed15
2025-05-14 15:06:02Giới thiệu Vietnam Aptos Hackathon Diễn ra từ tháng 5 đến tháng 7 năm 2025, Vietnam Aptos Hackathon là cuộc thi hackathon quy mô lớn được tổ chức trong khuôn khổ của sự kiện GM Vietnam | Vietnam Tech Week. Cuộc thi được đồng tổ chức bởi Aptos Foundation, SSID và Kyros Ventures, với sự đồng hành của các đối tác chiến lược như DoraHacks, Cloud Ace và AlphaTeam.
Vietnam Aptos Hackathon được kỳ vọng sẽ trở thành bệ phóng lý tưởng cho các builder, developer và sinh viên tại Việt Nam cũng như tại Đông Nam Á để hiện thực hóa những ý tưởng Web3 đột phá trên Aptos — blockchain Layer-1 thế hệ mới, được thiết kế tối ưu cho tốc độ xử lý, bảo mật mạnh mẽ và khả năng mở rộng vượt trội.
Chủ đề và Thử thách Vietnam Aptos Hackathon 2025 tập trung vào trọng tâm chính, định hình tương lai trên hệ sinh thái Aptos, bao gồm:
Web3 Consumer: Phát triển các ứng dụng hướng đến người dùng đại chúng như Prediction Markets, SocialFi, GameFi, NFT và Art & Culture.
Payments & Finance: Xây dựng hệ thống thanh toán thời gian thực, mô hình micro-loans, giải pháp token hóa tài sản (RWAs), cùng các sản phẩm tài chính phi tập trung.
Decentralized Infrastructure: Tạo lập nền tảng hạ tầng phi tập trung, từ công cụ tích hợp AI/ML, oracle đến các giải pháp phân phối nội dung hiệu quả. Tổng giải thưởng hơn 400.000 USD Vietnam Aptos Hackathon 2025 mang đến cơ cấu giải thưởng hấp dẫn cùng nhiều cơ hội phát triển sau cuộc thi nhằm hỗ trợ các đội thi tiếp tục mở rộng sản phẩm và kết nối với hệ sinh thái Web3 trên Aptos.
Top 5 đội thi xuất sắc nhất sẽ nhận được các phần thưởng giá trị để tiếp tục mở rộng sản phẩm sau cuộc thi. Cụ thể:
Giải Nhất: 200.000 USD Google Cloud Credits, 50.000 USD Build Aptos Credits và 10.000 USD tiền mặt.
Giải Nhì & Ba: Mỗi đội nhận được 100.000 USD Google Cloud Credits, 25.000 USD Build Aptos Credits cùng 10.000 USD tiền mặt.
Giải Tư & Năm: Quà tặng đặc biệt từ ban tổ chức, chứng nhận chính thức và 10.000 USD tiền mặt để tiếp tục hành trình phát triển sản phẩm. Bên cạnh đó, Vietnam Aptos Hackathon 2025 cũng dành riêng hạng mục đặc biệt cho sinh viên để thế hệ builder trẻ thể hiện tài năng, tiếp cận công nghệ Web3 tiên tiến. Cụ thể:
Top 5 đội sinh viên: Mỗi đội sẽ nhận 2.000 USD tiền mặt.
Top 2 đội xuất sắc nhất: Được trình bày dự án trực tiếp trên sân khấu chính trong ngày Demo Day.
Tất cả đội sinh viên tham gia đều nhận được chứng nhận chính thức từ chương trình. Bên cạnh các giải thưởng tiền mặt và tài nguyên kỹ thuật, Vietnam Aptos Hackathon 2025 còn mang đến nhiều cơ hội hỗ trợ phát triển dành cho các đội thi sau khi chương trình kết thúc.
Tất cả các đội sẽ nhận được hỗ trợ trực tiếp từ đội ngũ kỹ thuật của Aptos Foundation và các đối tác chiến lược trong hệ sinh thái. Đặc biệt, ngoài cơ cấu giải thưởng chính, các đội còn có cơ hội được pitch trực tiếp để nhận thêm fast-track grants từ Aptos Foundation.
Đáng chú ý, các đội thi còn được mời tham gia vào buổi private-dinner để gặp gỡ ban lãnh đạo Aptos Foundation và các quỹ đầu tư lớn, tạo điều kiện kết nối trực tiếp.
Chi tiết tham gia đăng kí và lịch trình cuộc thi Để trở thành một phần của hành trình Vietnam Aptos Hackathon 2025. Builder tham gia đăng kí tại đây:https://dorahacks.io/hackathon/vietnamaptoshackathon/detail
Lịch trình Vietnam Aptos Hackathon diễn ra như sau:
Từ ngày 14/05: Mở đơn đăng ký tham dự
14/05 – 19/06: Chuỗi workshop university tour và các buổi AMA
19/06 – 18/07: Trainning online/offline, nộp bài dự thi và tham gia Founder Dinner
21/07 – 25/07: Đánh giá sơ khảo và lựa chọn đội vào vòng chung kết
02/08: Chung kết & Trao giải trực tiếp tại sự kiện GM Vietnam Sự kiện sẽ kết thúc bằng Demo Day tại GM Vietnam 2025 (ngày 02/08) với sự tham dự của các quỹ đầu tư hàng đầu và lãnh đạo Aptos Foundation.
Tham gia Vietnam Aptos Hackathon 2025 Vietnam Aptos Hackathon chào đón mọi đối tượng: từ sinh viên đến các đội ngũ startup dày dạn kinh nghiệm. Nếu bạn đang xây dựng một ứng dụng Web3, đừng bỏ lỡ cơ hội tham gia cuộc thi nhận tài trợ, kết nối và ghi dấu ấn tại một trong những blockchain Layer 1 nổi bật nhất hiện nay.
-
 @ 615d5a95:c3b79c24
2025-05-14 10:49:22
@ 615d5a95:c3b79c24
2025-05-14 10:49:22HI365 ra đời như một nền tảng trực tuyến hoàn hảo, đáp ứng mọi nhu cầu giải trí và phát triển kỹ năng của người dùng trong một không gian số hiện đại. Với giao diện được thiết kế tinh tế, dễ sử dụng và tối ưu hóa cho mọi thiết bị, từ điện thoại di động đến máy tính để bàn, HI365 mang đến trải nghiệm mượt mà và đầy tiện ích cho người tham gia. Nền tảng này chú trọng vào việc mang lại sự linh hoạt trong việc truy cập và tương tác, giúp người dùng dễ dàng tìm kiếm và tham gia vào các hoạt động phù hợp với sở thích và nhu cầu cá nhân. Bên cạnh đó, HI365 cung cấp một hệ thống cá nhân hóa thông minh, cho phép người dùng tùy chỉnh trải nghiệm của mình sao cho phù hợp nhất, từ việc tham gia các hoạt động sáng tạo cho đến thử thách khả năng phân tích và quyết định. Những tính năng này giúp tạo nên một không gian trực tuyến không chỉ giải trí mà còn mang lại giá trị thực sự cho người tham gia.
Một trong những điểm mạnh của HI365 là cộng đồng người dùng thân thiện và năng động, nơi mọi người có thể chia sẻ những kinh nghiệm, học hỏi lẫn nhau và cùng nhau phát triển. Với hệ thống kết nối linh hoạt và các tính năng tương tác hiệu quả, HI365 không chỉ là nơi để giải trí mà còn là không gian để người dùng nâng cao kỹ năng và tư duy chiến lược. Các hoạt động tại HI365 được thiết kế khoa học, dễ tiếp cận nhưng không thiếu sự thử thách, giúp người dùng rèn luyện sự nhạy bén trong quyết định và khả năng phân tích tình huống. Cộng đồng tại HI365 luôn duy trì sự cạnh tranh lành mạnh và động viên lẫn nhau phát triển, từ đó tạo ra môi trường học hỏi và sáng tạo không ngừng. Những tính năng như bảng xếp hạng, sự kiện đặc biệt hay các cuộc thi trực tuyến giúp gia tăng tính hấp dẫn và thú vị, đồng thời thúc đẩy người dùng phát triển không chỉ về kỹ năng mà còn về mặt tư duy sáng tạo.
Không chỉ chú trọng đến trải nghiệm người dùng và sự phát triển cộng đồng, HI365 còn cam kết mang lại một môi trường an toàn và bảo mật cho tất cả người tham gia. Được trang bị hệ thống bảo mật tiên tiến, HI365 bảo vệ thông tin người dùng một cách tuyệt đối, giúp người tham gia yên tâm tận hưởng những hoạt động mà không phải lo lắng về các vấn đề bảo mật. Đội ngũ hỗ trợ khách hàng chuyên nghiệp luôn sẵn sàng giải đáp thắc mắc và hỗ trợ người dùng 24/7, đảm bảo mọi trải nghiệm tại nền tảng này luôn suôn sẻ và trọn vẹn. Với những tính năng liên tục được cải tiến, HI365 không ngừng nâng cao chất lượng dịch vụ để đáp ứng nhu cầu ngày càng cao của người dùng. Những cải tiến này không chỉ giúp tối ưu hóa trải nghiệm mà còn làm phong phú thêm các lựa chọn và hoạt động mà nền tảng mang lại. Nhờ vậy, HI365 không chỉ là một nền tảng giải trí mà còn là nơi giúp người dùng phát triển và rèn luyện những kỹ năng quan trọng trong cuộc sống.
-
 @ 8b19a626:6da35f21
2025-05-14 09:07:19
@ 8b19a626:6da35f21
2025-05-14 09:07:19I did not arrive with loud words, just quiet prayers and a heart full of purpose. Queen Marvel looked beyond the surface, she saw not where I stood but where I could go to_ to perform in global stages. She believed in me when I was still uncertain, still learning how to grow. She didn't offer gold, she offered faith, a silent kind of power that says," I see you", even when the world doesn't yet. And now, there is a community behind me, Eyes full of hope, hearts whispering, do not forget us. I carry their dreams like sacred cargo. I talk Bitcoin but I live poetry, now am schooling folks with metaphors and memes. Dropping bars on blocks and dreams, telling kings and queens, you got value, you got choice. So here is to Bitcoin, the rebel code that broke my chains, that gave me freedom and these golden poetic veins. This is not hype, it is truth in rhyme Now I spit not for fame But to light other flames, cos if it unlocked mine, then you can do the same. MaKiNi
-
 @ 6389be64:ef439d32
2025-02-27 21:32:12
@ 6389be64:ef439d32
2025-02-27 21:32:12GA, plebs. The latest episode of Bitcoin And is out, and, as always, the chicanery is running rampant. Let’s break down the biggest topics I covered, and if you want the full, unfiltered rant, make sure to listen to the episode linked below.
House Democrats’ MEME Act: A Bad Joke?
House Democrats are proposing a bill to ban presidential meme coins, clearly aimed at Trump’s and Melania’s ill-advised token launches. While grifters launching meme coins is bad, this bill is just as ridiculous. If this legislation moves forward, expect a retaliatory strike exposing how politicians like Pelosi and Warren mysteriously amassed their fortunes. Will it pass? Doubtful. But it’s another sign of the government’s obsession with regulating everything except itself.
Senate Banking’s First Digital Asset Hearing: The Real Target Is You
Cynthia Lummis chaired the first digital asset hearing, and—surprise!—it was all about control. The discussion centered on stablecoins, AML, and KYC regulations, with witnesses suggesting Orwellian measures like freezing stablecoin transactions unless pre-approved by authorities. What was barely mentioned? Bitcoin. They want full oversight of stablecoins, which is really about controlling financial freedom. Expect more nonsense targeting self-custody wallets under the guise of stopping “bad actors.”
Bank of America and PayPal Want In on Stablecoins
Bank of America’s CEO openly stated they’ll launch a stablecoin as soon as regulation allows. Meanwhile, PayPal’s CEO paid for a hat using Bitcoin—not their own stablecoin, Pi USD. Why wouldn’t he use his own product? Maybe he knows stablecoins aren’t what they’re hyped up to be. Either way, the legacy financial system is gearing up to flood the market with stablecoins, not because they love crypto, but because it’s a tool to extend U.S. dollar dominance.
MetaPlanet Buys the Dip
Japan’s MetaPlanet issued $13.4M in bonds to buy more Bitcoin, proving once again that institutions see the writing on the wall. Unlike U.S. regulators who obsess over stablecoins, some companies are actually stacking sats.
UK Expands Crypto Seizure Powers
Across the pond, the UK government is pushing legislation to make it easier to seize and destroy crypto linked to criminal activity. While they frame it as going after the bad guys, it’s another move toward centralized control and financial surveillance.
Bitcoin Tools & Tech: Arc, SatoChip, and Nunchuk
Some bullish Bitcoin developments: ARC v0.5 is making Bitcoin’s second layer more efficient, SatoChip now supports Taproot and Nostr, and Nunchuk launched a group wallet with chat, making multisig collaboration easier.
The Bottom Line
The state is coming for financial privacy and control, and stablecoins are their weapon of choice. Bitcoiners need to stay focused, keep their coins in self-custody, and build out parallel systems. Expect more regulatory attacks, but don’t let them distract you—just keep stacking and transacting in ways they can’t control.
🎧 Listen to the full episode here: https://fountain.fm/episode/PYITCo18AJnsEkKLz2Ks
💰 Support the show by boosting sats on Podcasting 2.0! and I will see you on the other side.
-
 @ 04c915da:3dfbecc9
2025-02-25 03:55:08
@ 04c915da:3dfbecc9
2025-02-25 03:55:08Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 961e8955:d7fa53e4
2025-05-14 08:52:07
@ 961e8955:d7fa53e4
2025-05-14 08:52:07 Cryptocurrencies have become increasingly popular in recent years, and their impact on the world economy is a topic of much discussion. While there are many potential benefits to using cryptocurrencies, such as greater privacy and security, there are also several ways in which they may impact the global economy.
Cryptocurrencies have become increasingly popular in recent years, and their impact on the world economy is a topic of much discussion. While there are many potential benefits to using cryptocurrencies, such as greater privacy and security, there are also several ways in which they may impact the global economy.One potential impact of cryptocurrencies on the world economy is their ability to disrupt traditional financial systems. By enabling peer-to-peer transactions without the need for intermediaries such as banks or financial institutions, cryptocurrencies have the potential to lower transaction costs and increase efficiency. This could have a significant impact on industries such as remittances, where people send money across borders to their families.
However, the rise of cryptocurrencies has also brought concerns around their potential impact on monetary policy. Because cryptocurrencies are decentralized and not subject to government control, some fear that they could lead to increased volatility and instability in financial markets. Additionally, the use of cryptocurrencies could make it more difficult for central banks to control inflation and regulate the money supply.
Another potential impact of cryptocurrencies on the global economy is their ability to facilitate international trade. With the use of blockchain technology, cryptocurrencies could provide a secure and transparent means of conducting cross-border transactions. This could reduce the costs and time associated with traditional international payments, which could have a positive impact on global trade.
Finally, the growth of cryptocurrencies could also have an impact on wealth distribution. Because cryptocurrencies are accessible to anyone with an internet connection, they could provide new opportunities for people who have been excluded from traditional financial systems. However, there are also concerns that the concentration of wealth in the hands of early adopters and large cryptocurrency holders could exacerbate existing inequalities.
In conclusion, the impact of cryptocurrencies on the world economy is complex and multifaceted. While they have the potential to disrupt traditional financial systems and facilitate international trade, they also raise concerns around monetary policy and wealth distribution. As the use of cryptocurrencies continues to grow, it will be important to carefully monitor their impact on the global economy and take steps to address any potential risks.
-
 @ 6e0ea5d6:0327f353
2025-02-21 18:15:52
@ 6e0ea5d6:0327f353
2025-02-21 18:15:52"Malcolm Forbes recounts that a lady, wearing a faded cotton dress, and her husband, dressed in an old handmade suit, stepped off a train in Boston, USA, and timidly made their way to the office of the president of Harvard University. They had come from Palo Alto, California, and had not scheduled an appointment. The secretary, at a glance, thought that those two, looking like country bumpkins, had no business at Harvard.
— We want to speak with the president — the man said in a low voice.
— He will be busy all day — the secretary replied curtly.
— We will wait.
The secretary ignored them for hours, hoping the couple would finally give up and leave. But they stayed there, and the secretary, somewhat frustrated, decided to bother the president, although she hated doing that.
— If you speak with them for just a few minutes, maybe they will decide to go away — she said.
The president sighed in irritation but agreed. Someone of his importance did not have time to meet people like that, but he hated faded dresses and tattered suits in his office. With a stern face, he went to the couple.
— We had a son who studied at Harvard for a year — the woman said. — He loved Harvard and was very happy here, but a year ago he died in an accident, and we would like to erect a monument in his honor somewhere on campus.— My lady — said the president rudely —, we cannot erect a statue for every person who studied at Harvard and died; if we did, this place would look like a cemetery.
— Oh, no — the lady quickly replied. — We do not want to erect a statue. We would like to donate a building to Harvard.
The president looked at the woman's faded dress and her husband's old suit and exclaimed:
— A building! Do you have even the faintest idea of how much a building costs? We have more than seven and a half million dollars' worth of buildings here at Harvard.
The lady was silent for a moment, then said to her husband:
— If that’s all it costs to found a university, why don’t we have our own?
The husband agreed.
The couple, Leland Stanford, stood up and left, leaving the president confused. Traveling back to Palo Alto, California, they established there Stanford University, the second-largest in the world, in honor of their son, a former Harvard student."
Text extracted from: "Mileumlivros - Stories that Teach Values."
Thank you for reading, my friend! If this message helped you in any way, consider leaving your glass “🥃” as a token of appreciation.
A toast to our family!
-
 @ eab58da0:eebdafbf
2025-05-14 08:19:47
@ eab58da0:eebdafbf
2025-05-14 08:19:47By Unknownfx
As a writer with over 100 stories published on platforms like Medium, I’ve explored countless spaces to share my voice. Few, however, have captured my heart quite like YakiHonne. This platform blends the best of creative expression, community engagement, and versatility, making it a perfect fit for someone like me, whose work spans self-improvement articles and forex/crypto trading posts. Below, I’ll dive into why YakiHonne has become my go-to platform, from its seamless writing experience to its vibrant, X-like social features.
A Writer’s Paradise for Self-Improvement and Mental Health Writing about self-improvement and mental health requires a space that feels safe, inspiring, and receptive. YakiHonne delivers exactly that. The platform’s clean interface and intuitive design make it easy to craft long-form articles that resonate with readers. Whether I’m sharing strategies for managing anxiety or tips for personal growth, YakiHonne’s formatting tools allow me to structure my thoughts clearly with headings, lists, and emphasis—perfect for breaking down complex topics into digestible insights.
What sets YakiHonne apart is its supportive community. Readers on the platform are genuinely engaged, leaving thoughtful comments that spark meaningful conversations. For instance, after posting an article on mindfulness techniques, I received feedback from readers who shared how my words helped them navigate tough days. This kind of connection fuels my passion for writing and reminds me why I focus on mental health and self-improvement. Unlike other platforms where articles can feel like they’re shouting into the void, YakiHonne makes every piece feel like a dialogue.
The X-Like Social Vibe: Notes, Quotes, and Instant Feedback One of my favorite features of YakiHonne is its resemblance to X, particularly in its note-posting and interaction mechanics. As someone who posts regularly about forex and crypto trading, I love the ability to share quick, bite-sized insights—market trends, trading psychology tips, or even a heads-up about a volatile crypto coin. These notes are like X posts: short, punchy, and designed to spark immediate engagement. The “quote” and “like” buttons add a layer of interactivity that makes posting feel dynamic and rewarding.
For example, when I shared a post about the importance of risk management in forex trading on X, it was quoted by several users who added their own perspectives, creating a mini-discussion thread. This instant feedback loop keeps me motivated to post regularly and I am seeing the same thing happening here. It’s also a great way to test ideas before turning them into full articles. The X-like social features make YakiHonne a hybrid platform—part writing hub, part social network—perfect for balancing my long-form self-improvement content with my trading-focused posts.
Versatility for My Dual Niches YakiHonne’s flexibility is a game-changer for someone like me with two distinct niches. My self-improvement and mental health articles require depth and storytelling, which YakiHonne’s article editor supports beautifully. Meanwhile, my forex and crypto trading posts thrive in the fast-paced, conversational note format. The platform doesn’t force me to choose between these worlds; instead, it gives me tools to excel in both.
This versatility also extends to audience reach. YakiHonne’s algorithm seems to understand my niches, recommending my articles to readers interested in personal growth and my notes to those following trading topics. This targeted exposure has helped me build a diverse following, something I struggled with on other platforms where my content sometimes got lost in the noise.
A Community That Feels Like Home Beyond the technical perks, YakiHonne’s community feels like a digital home. Writers and readers alike are passionate, curious, and supportive. I’ve connected with other creators who share my interests, from mental health advocates to trading enthusiasts. These connections have led to collaborations, like guest posts and even a few trading strategy discussions that inspired new content. The sense of belonging on YakiHonne is unmatched, making it a platform where I feel seen and valued as a writer.
Gratitude and Ambition: My YakiHonne Journey I’m endlessly grateful for discovering YakiHonne. It’s a platform that not only amplifies my voice but also aligns perfectly with my creative and social needs. As I continue to share my self-improvement articles and trading posts, I’m excited to grow my presence on YakiHonne, just as I’ve done on Medium and other platforms. My goal is to reach the top, building a loyal audience and making a lasting impact. With YakiHonne’s unique blend of features and community spirit, I’m confident this is just the beginning of an incredible journey.
-
 @ fd208ee8:0fd927c1
2025-02-15 07:02:08
@ fd208ee8:0fd927c1
2025-02-15 07:02:08E-cash are coupons or tokens for Bitcoin, or Bitcoin debt notes that the mint issues. The e-cash states, essentially, "IoU 2900 sats".
They're redeemable for Bitcoin on Lightning (hard money), and therefore can be used as cash (softer money), so long as the mint has a good reputation. That means that they're less fungible than Lightning because the e-cash from one mint can be more or less valuable than the e-cash from another. If a mint is buggy, offline, or disappears, then the e-cash is unreedemable.
It also means that e-cash is more anonymous than Lightning, and that the sender and receiver's wallets don't need to be online, to transact. Nutzaps now add the possibility of parking transactions one level farther out, on a relay. The same relays that cannot keep npub profiles and follow lists consistent will now do monetary transactions.
What we then have is * a transaction on a relay that triggers * a transaction on a mint that triggers * a transaction on Lightning that triggers * a transaction on Bitcoin.
Which means that every relay that stores the nuts is part of a wildcat banking system. Which is fine, but relay operators should consider whether they wish to carry the associated risks and liabilities. They should also be aware that they should implement the appropriate features in their relay, such as expiration tags (nuts rot after 2 weeks), and to make sure that only expired nuts are deleted.
There will be plenty of specialized relays for this, so don't feel pressured to join in, and research the topic carefully, for yourself.
https://github.com/nostr-protocol/nips/blob/master/60.md
-
 @ 0fa80bd3:ea7325de
2025-02-14 23:24:37
@ 0fa80bd3:ea7325de
2025-02-14 23:24:37intro
The Russian state made me a Bitcoiner. In 1991, it devalued my grandmother's hard-earned savings. She worked tirelessly in the kitchen of a dining car on the Moscow–Warsaw route. Everything she had saved for my sister and me to attend university vanished overnight. This story is similar to what many experienced, including Wences Casares. The pain and injustice of that time became my first lessons about the fragility of systems and the value of genuine, incorruptible assets, forever changing my perception of money and my trust in government promises.
In 2014, I was living in Moscow, running a trading business, and frequently traveling to China. One day, I learned about the Cypriot banking crisis and the possibility of moving money through some strange thing called Bitcoin. At the time, I didn’t give it much thought. Returning to the idea six months later, as a business-oriented geek, I eagerly began studying the topic and soon dove into it seriously.
I spent half a year reading articles on a local online journal, BitNovosti, actively participating in discussions, and eventually joined the editorial team as a translator. That’s how I learned about whitepapers, decentralization, mining, cryptographic keys, and colored coins. About Satoshi Nakamoto, Silk Road, Mt. Gox, and BitcoinTalk. Over time, I befriended the journal’s owner and, leveraging my management experience, later became an editor. I was drawn to the crypto-anarchist stance and commitment to decentralization principles. We wrote about the economic, historical, and social preconditions for Bitcoin’s emergence, and it was during this time that I fully embraced the idea.
It got to the point where I sold my apartment and, during the market's downturn, bought 50 bitcoins, just after the peak price of $1,200 per coin. That marked the beginning of my first crypto winter. As an editor, I organized workflows, managed translators, developed a YouTube channel, and attended conferences in Russia and Ukraine. That’s how I learned about Wences Casares and even wrote a piece about him. I also met Mikhail Chobanyan (Ukrainian exchange Kuna), Alexander Ivanov (Waves project), Konstantin Lomashuk (Lido project), and, of course, Vitalik Buterin. It was a time of complete immersion, 24/7, and boundless hope.
After moving to the United States, I expected the industry to grow rapidly, attended events, but the introduction of BitLicense froze the industry for eight years. By 2017, it became clear that the industry was shifting toward gambling and creating tokens for the sake of tokens. I dismissed this idea as unsustainable. Then came a new crypto spring with the hype around beautiful NFTs – CryptoPunks and apes.
I made another attempt – we worked on a series called Digital Nomad Country Club, aimed at creating a global project. The proceeds from selling images were intended to fund the development of business tools for people worldwide. However, internal disagreements within the team prevented us from completing the project.
With Trump’s arrival in 2025, hope was reignited. I decided that it was time to create a project that society desperately needed. As someone passionate about history, I understood that destroying what exists was not the solution, but leaving everything as it was also felt unacceptable. You can’t destroy the system, as the fiery crypto-anarchist voices claimed.
With an analytical mindset (IQ 130) and a deep understanding of the freest societies, I realized what was missing—not only in Russia or the United States but globally—a Bitcoin-native system for tracking debts and financial interactions. This could return control of money to ordinary people and create horizontal connections parallel to state systems. My goal was to create, if not a Bitcoin killer app, then at least to lay its foundation.
At the inauguration event in New York, I rediscovered the Nostr project. I realized it was not only technologically simple and already quite popular but also perfectly aligned with my vision. For the past month and a half, using insights and experience gained since 2014, I’ve been working full-time on this project.
-
 @ a3c6f928:d45494fb
2025-05-14 07:44:43
@ a3c6f928:d45494fb
2025-05-14 07:44:43Freedom of expression is one of the cornerstones of any open and progressive society. It is the right to speak, write, and share ideas without fear of censorship or persecution. More than just a legal right, it is a vital part of human development and societal growth.
Understanding Freedom of Expression
Freedom of expression goes beyond merely speaking your mind. It includes the right to seek, receive, and impart information and ideas of all kinds, whether verbally, in writing, through art, or in any other medium of expression. It is a right that fuels debate, drives change, and challenges injustice.
The Power of a Voice
Throughout history, freedom of expression has been a powerful tool for social change. From the speeches of Martin Luther King Jr. to the writings of Nelson Mandela, the ability to express ideas freely has sparked revolutions, reformed societies, and inspired generations.
Challenges to Freedom of Expression
Despite its importance, freedom of expression is often threatened. Censorship, political suppression, and societal pressures can silence voices that challenge the status quo. In the digital age, misinformation and online harassment also pose new challenges to maintaining this fundamental right.
Protecting the Right to Speak
-
Support Open Dialogue: Encourage discussions, even when opinions differ.
-
Stand Against Censorship: Oppose efforts to silence voices, regardless of their viewpoint.
-
Promote Media Literacy: Equip people to identify credible information and resist manipulation.
-
Respect Diverse Opinions: Embrace different perspectives, even if you disagree.
The Path Forward
Freedom of expression is not just about the right to speak; it's about the right to be heard. By protecting this freedom, we safeguard democracy, encourage innovation, and foster an environment where truth can flourish.
“I disapprove of what you say, but I will defend to the death your right to say it.” — Evelyn Beatrice Hall
Speak boldly. Listen openly. Protect the right to be heard.
-
-
 @ 961e8955:d7fa53e4
2025-05-14 07:02:41
@ 961e8955:d7fa53e4
2025-05-14 07:02:41Medical billing and coding play a crucial role in the healthcare industry. Healthcare facilities and insurance companies rely on skilled professionals to accurately code medical procedures and submit claims for reimbursement.
If you're interested in pursuing a career in medical billing and coding, online schools offer a convenient and flexible option to learn the necessary skills. Here is a detailed list of some of the top online schools for medical billing and coding:
Penn Foster College: Penn Foster College offers an online associate degree program in medical billing and coding that covers topics such as anatomy and physiology, medical terminology, and healthcare law and ethics. The program is self-paced, allowing students to complete it at their own pace.
Ultimate Medical Academy: Ultimate Medical Academy offers an online diploma program in medical billing and coding that can be completed in as little as 10 months. The program covers topics such as medical office management, medical coding, and healthcare reimbursement.
Herzing University: Herzing University offers an online associate degree program in medical billing and insurance coding that can be completed in as little as 20 months. The program covers topics such as medical billing, medical coding, and healthcare reimbursement.
Ashworth College: Ashworth College offers an online diploma program in medical billing and coding that can be completed in as little as four months. The program covers topics such as medical terminology, medical coding, and healthcare law and ethics.
Career Step: Career Step offers an online certificate program in medical billing and coding that can be completed in as little as four months. The program covers topics such as medical terminology, anatomy and physiology, and medical coding.
These online schools offer a range of programs to meet the needs of aspiring medical billing and coding professionals. With the flexibility and convenience of online learning, you can gain the skills and knowledge you need to start a rewarding career in this growing field.
Average Salaries for Medical Billing and Coding Professionals in the United States Medical billing and coding salaries can vary depending on several factors such as location, experience, and certification. Here is a general list of average salaries for medical billing and coding professionals in the United States:
Medical billing and coding specialist: $42,640 per year Medical records technician: $44,020 per year Medical coder: $49,780 per year Medical billing specialist: $41,750 per year Certified coding specialist: $61,620 per year It's important to note that these are average salaries and may vary based on individual circumstances. Additionally, pursuing advanced certification and further education can lead to higher salaries and opportunities for career advancement.
The Future of Medical Billing and Coding Careers: Job Outlook and Growth Potential The demand for skilled medical billing and coding professionals is expected to grow in the coming years. According to the Bureau of Labor Statistics, employment of health information technicians (which includes medical billing and coding professionals) is projected to grow 8 percent from 2019 to 2029, much faster than the average for all occupations.
Medical billing and coding professionals can work in a variety of settings, including hospitals, clinics, physician's offices, and insurance companies. They play a critical role in ensuring accurate documentation and reimbursement for medical services.
In addition to traditional employment opportunities, medical billing and coding professionals can also work as freelancers or start their own businesses. With the rise of telemedicine and remote work, there may be even more opportunities for individuals to work from home in this field.
Overall, the job outlook for medical billing and coding professionals is promising, with a variety of employment opportunities available in the healthcare industry.
Where Can You Work with a Medical Billing and Coding Certification? Medical billing and coding professionals can work in various healthcare settings, such as:
Hospitals Clinics and outpatient centers Physician's offices Insurance companies Government agencies Nursing homes and long-term care facilities Home healthcare agencies Medical billing and coding companies Telemedicine companies Additionally, with the rise of remote work and telemedicine, medical billing and coding professionals may have the opportunity to work from home or as freelancers. This flexibility allows for a more diverse range of employment options and can provide greater work-life balance.
-
 @ 9e69e420:d12360c2
2025-02-17 17:12:01
@ 9e69e420:d12360c2
2025-02-17 17:12:01President Trump has intensified immigration enforcement, likening it to a wartime effort. Despite pouring resources into the U.S. Immigration and Customs Enforcement (ICE), arrest numbers are declining and falling short of goals. ICE fell from about 800 daily arrests in late January to fewer than 600 in early February.
Critics argue the administration is merely showcasing efforts with ineffectiveness, while Trump seeks billions more in funding to support his deportation agenda. Increased involvement from various federal agencies is intended to assist ICE, but many lack specific immigration training.
Challenges persist, as fewer immigrants are available for quick deportation due to a decline in illegal crossings. Local sheriffs are also pressured by rising demands to accommodate immigrants, which may strain resources further.
-
 @ 502ab02a:a2860397
2025-05-14 06:36:13
@ 502ab02a:a2860397
2025-05-14 06:36:13ย้อนกลับไปในยุคโบราณ ไม่ว่าชนเผ่าชาวทุ่งหญ้าในยูเรเชีย ชาวอินเดียตอนเหนือ หรือเผ่าทะเลทรายแถบตะวันออกกลาง ล้วนมีวัฒนธรรมที่เกี่ยวข้องกับนมวัว นมจามรี นมแพะ และทุกชนิดก็ลงเอยที่การเอานมไปแปรรูปเป็น “เนย” ทั้งเนยแบบสด เนยหมัก
เนยที่เก่าแก่ที่สุดเท่าที่มีบันทึก คือ “Bog Butter” จากไอร์แลนด์ ไม่ใช่ blockbuster นะ ฮาๆๆๆ “Bog Butter” เป็นเนยที่ถูกฝังไว้ในบึงพรุ (bog) ของไอร์แลนด์และสก็อตแลนด์ มาหลายร้อยถึงหลายพันปี โดยไม่มีการเน่าเสีย! เพราะบึงพรุมีสภาพแวดล้อมที่เป็นกรด ไม่มีออกซิเจน และเย็น จึงเป็นสภาวะที่เหมาะกับการถนอมอาหารแบบธรรมชาติสุด ๆ
มีหลักฐานการค้นพบ Bog Butter อายุราว 3,000 ปี (ยุคเหล็กตอนต้น) ในหลายพื้นที่ของไอร์แลนด์ เช่น County Offaly, County Cavan และ County Fermanagh ลักษณะของ Bog Butter ที่ขุดพบ บางก้อนยังอยู่ในสภาพดี มีสีเหลืองทอง เนื้อเนียน และยังมีกลิ่นคล้ายชีสที่สุกมาก ๆ ภาชนะที่ใช้ใส่เนยมักเป็นถังไม้ กล่องไม้โอ๊ค หรือแม้แต่หนังสัตว์ผูกไว้แน่น ๆ
นักโบราณคดีเชื่อว่า Bog Butter คือเนยจากนมสัตว์ (นมวัวหรือนมแพะ) ที่อาจผ่านการหมักหรือเคี่ยวแล้วก่อนนำไปฝัง เพื่อถนอมไว้กินในฤดูหนาวหรือในปีที่น้ำนมขาดแคลน บางทฤษฎีก็เสนอว่ามีการฝังเนยเพื่อเหตุผลทางพิธีกรรม หรือใช้เป็น “ทรัพย์สิน” ที่ฝากไว้กับแผ่นดินเพื่อแสดงความมั่งคั่ง
ที่น่าทึ่งก็คือนี่เป็นการถนอมเนยที่ไม่ใช้ความร้อน ไม่ใช้เกลือ และไม่ใช้น้ำแข็ง แต่กลับอยู่ได้นานเป็นพันปี เพราะอาศัยสภาพแวดล้อมที่เข้าใจธรรมชาติสุด ๆ มีข้อมูลว่าเขามีการชิม Bog Butter ที่ขุดขึ้นมาด้วยนะ มีคำบรรยายไว้ว่า “มันมีกลิ่นชีสเข้มข้น กลิ่นดินและควันบาง ๆ เหมือนกินประวัติศาสตร์” 5555
เนยแท้ (butter) ก็คือน้ำนมที่ถูกแยกเอาไขมันออกมาด้วยการตี (churning) โดยอาศัยแรงมือหรือแรงกล เครื่องตีจะรวมเม็ดไขมันเล็ก ๆ จากครีมนมให้จับตัวกันกลายเป็นก้อนเนย แล้วแยกเอาน้ำบัตเตอร์มิลค์ออกไป คงเหลือไว้แค่ไขมันเนยที่หอม มัน และอุดมไปด้วยวิตามิน A, D, E, K ในรูปที่ดูดซึมง่าย เพราะละลายในไขมัน
องค์ประกอบหลักที่อยู่ในเนยจะมี 3 ส่วนใหญ่ๆเรียกแบบเหมารวมคือ
1 ไขมันนม/ไขมันเนย หรือ butter oil 2 เนื้อนม หรือ solid milk 3 ส่วนที่เป็นของเหลวต่างๆ หรือ moisture คือมันไม่เจาะจงว่าน้ำนึกออกไหมครับ นมมาจากธรรมชาติไม่ได้มาจากการผสมสัดส่วน ดังนั้นการจะมุ่งว่าเป็นน้ำเลยจึงไม่ใช่เสียทีเดียว ภาษาไทยเราจึงมักแปลไว้ว่าส่วนที่เป็นความชื้น *ตรงนี้มีหมายเหตุไว้นิดหน่อยครับว่า เจ้าไขมันเนยนี่ เราอาจะเจอภาษาอังกฤษหลายคำนะครับ เช่น butterfat, butter oil, fat milk ตรงนี้ให้เข้าไจไว้ว่ามันหมายถึงสิ่งเดียวกันนั่นหละครับ
สิ่งสำคัญในการทำเนยคือ ไขมันจากนมนั่นเอง นมส่วนที่ไขมันสูงนั้นเราเรียกว่า ครีม นึกภาพเป็นการ์ตูนง่ายๆได้ว่า เราช้อนเเอาเฉพาะส่วนที่เป็นครีมนั่นแหละ แล้วเอามาทำมาทำเป็นเนย ปล่อยทิ้งส่วนของนมที่ไม่มีไขมันเอาไว้ทำอย่างอื่น (มันคือนมพร่องมันเนย คุ้นมะ แต่จริงๆเค้าไม่ได้เอาส่วนนี้มาขายเป็นนมให้เราหรอกนะครับ โรงงานแต่ละโรงจะตั้งไลน์ผลิตเพื่อสินค้าที่ดีที่สุดของตัวเอิง จะไม่จับฉ่ายเอาเศษเดนมาทำของขายให้เรา)
การเตรียมครีมก่อนจะเข้าสู่การผลิตเนยก็จะมีหลากหลายรูปแบบยกตัวอย่างเช่น
-Sour cream butter หรือ Cultured butter เป็นเนยทำจากครีมที่ผ่านการพาสเจอไรส์(ฆ่าเชื้อ) แล้วหมักด้วยจุลินทรีย์แลคติกหรือไม่ก็แลคโตบาซิลัส ทำให้มีกลิ่นและรสที่ดี -Neutralized sour cream butter เป็นเนยที่ได้จากครีมที่หมักด้วยจุลินทรีย์แล้วเอาไปทำเป็นกลางด้วย โซเดียมไบคาบอเนต โซเดียมคาร์บอเนต แคลเซียมไฮดรอกไซด์ รวมกับ แมกนีเซียมออกไซด์ หรือ แมกนีเซียมไฮดรอกไซด์ -Sweet cream butter เป็นเนยที่ทำจากครีมที่ผ่านการพาสเจอไรส์(ฆ่าเชื้อ) แต่ไม่มีการหมักบ่ม คือนำไปปั่นทำเนยเลย เนยชนิดนี้จะมีกลิ่นคล้ายครีมถ้ายี่ห้อนั้นๆไม่ได้เติมกลิ่นลงไปเพิ่มนะครับ รสชาติจะออกไปทางหวานนิดๆ เพราะมีน้ำตาลธรรมชาติในนมอยู่เนื่องจากไม่ได้ผ่านการหมัก แต่ไม่ต้องกังวลเพราะไม่ถึงกับหวานเวอร์ มันจะแค่หวานกว่าเนยชนิด Cultured butter แค่นั้น -Semi-culture butter หรือ European-style butter หรือ Fresh cream butter เป็นเนยที่ได้จากครีมที่ไม่ได้ผ่านการหมัก คือทำแบบเดียวกับ Sweet cream butter แต่ขั้นตอนสุดท้ายมีการเติมกลิ่นรสและกรดแลคติก ที่ได้จากนมหมักจุลินทรีย์แล้วเอาไปผ่านกระบวนการ อัลตร้าฟิลเทรชัน (Ultrafiltration) เพื่อให้เข้มข้นขึ้น -Raw butter cream เป็นเนยที่ผลิตจากน้ำนมดิบ ไม่ผ่านการพาสเจอไรส์(ฆ่าเชื้อ) คือจัดไปดิบๆเลย นมดิบสดๆมาแยกครีมแล้วปั่นทำเนยเลยไม่มีการเติมอะไรทั้งสิ้น คุณภาพของเนยชนิดนี้จะแปรผันตามคุณภาพของน้ำนมดิบและความเชี่ยวชาญของผู้ที่ผลิตเนย อายุของเนยชนิดนี้จะสั้นแค่ประมาณ 7-10วันเท่านั้นเพราะทุกอย่างมันสดจริงๆ
เห็นไหมครับว่า เนยแต่ละยี่ห้อเขาก็จะมีกรรมวิธีผลิตเนยในรูปแบบที่ต่างกันไป เนยบ่มก็จะมีกลิ่นหอมรสที่หนักแน่นปริมาณไขมันเนยและความชื้นน้อยกว่าเนยแบบ sweet cream ส่วนเจ้าเนย sweet cream เองก็เน้นที่ความสดความเฟรช กลิ่นเบาๆครีมๆมีความหวานหลงเหลืออยู่และมีราคาถูกกว่า ส่วนตัว raw butter ก็จะออกไปทางงานคราฟท์ คลาสสิค
เนย Home made ทำยังไง เนยแบบที่เราทำกินเองได้ในบ้านก็เป็นแบบ sweet cream butter หรือ เนยที่ได้จากครีมสดไม่ผ่านการหมักอะไรเลย เว้นแต่เติมเกลือเพื่อให้เป็นเนยเค็ม (จริงๆเติมเกลือเพื่อช่วยยืดอายุเนยได้อีกระยะหนึ่งด้วยนะ เป็นแทคติก) ปกติวิธีการทำเนย เขาจะเอาครีมเข้าถังปั่น เพื่อให้ครีมเกิดการแยกก้อนเนยเป็น grain (เขาเรียกว่า butter granule/butter curds) กับ หางเนย (butter milk) ซึ่งเป็นของเหลวที่ประกอบไปด้วยเนื้อนมไม่รวมมันเนยแล้วก็น้ำ แล้วเขาก็จะเอาก้อนเนยนี่แหละไปล้างน้ำเย็นเอากลิ่นหืนๆและรสประหลาดๆออกไป กำจัดความชื้นแล้วจบกระบวนการตีๆตบๆขึ้นรูปเนยก้อนต่อไป
ตรงนี้ถ้าจะให้เห็นภาพขึ้น ใครทำขนมเองคงรู้ดี เวลาที่เราตีวิปครีมมากเกินไป มันจะจับก้อนและแยกชั้น เป็นก้อนๆกับเหลวๆ ก้อนๆก็คือเนื้อเนย ไอ้เหลวๆก็คือ butter milk
การทำ เนยสด homemade fresh butter กินเองที่บ้านเราก็ทำได้ด้วยการจำลองถังปั่นด้วยเครื่องตีขนม จะเป็นแบบตีมือหรือแบบเครื่องก็ได้ครับ หรืออยากจะแอดวานซ์เอาใส่ขวดน้ำแล้วเขย่าก็ได้เหมือนกันนะครับ เมื่อถึงระยะเวลานึงครีมก็จะแยกตัวเป็นเนย กับ butter milk
ลองดูที่ผมเคยทำไว้ในคลิปนี้ได้ครับ https://youtu.be/bzo7V9n2cxc?si=0ZvcAT1H-6h1ZmUh
ไขมันในเนยมีองค์ประกอบพิเศษที่ไม่ค่อยถูกพูดถึงเท่าไรนัก นั่นคือกรดไขมันสายสั้นอย่าง butyric acid ซึ่งมีชื่อมาจากคำว่า “butter” เลย เพราะมันมีบทบาทในลำไส้ โดยเฉพาะการเป็นอาหารของเซลล์เยื่อบุลำไส้ใหญ่ ช่วยลดอาการอักเสบในระบบทางเดินอาหาร
สัดส่วนไขมันในเนยส่วนใหญ่จะเป็น ไขมันอิ่มตัว (SFA) ราว 50-65%, ไขมันไม่อิ่มตัวเชิงเดี่ยว (MUFA) ประมาณ 25-30% และไขมันไม่อิ่มตัวเชิงซ้อน (PUFA) ราว 2-5% เท่านั้น แต่ในส่วนของ PUFA นั้นมีความพิเศษเล็กน้อย ที่จะคุยในน้ำมันตัวต่อไปครับ
ในโลกตะวันตกโดยเฉพาะฝรั่งเศส อิตาลี และยุโรปตอนเหนือ เนยคือพระเอกประจำห้องครัว ใช้ผัด ใช้อบ ใช้ทาขนมปัง เป็นของคู่กับวัฒนธรรมการกินแบบ traditional food ซึ่งแตกต่างจากยุคอุตสาหกรรมที่ผลักให้เนยแท้หลบมุม แล้วเอา margarine หรือ shortening ซึ่งเต็มไปด้วยไขมันแปรรูปมาแทน ด้วยการโฆษณาแบบ fiat food คล้ายกับเรื่องที่เฮียเคยพูดบ่อย ๆ นั่นแหละ
ในประเทศไทยเราเองก็มีเนยวัวใช้ในอาหารบางชนิด โดยเฉพาะขนมอบ ขนมฝรั่งโบราณ หรือขนมเนยสดสไตล์ยุโรปที่เข้ามาสมัยรัชกาลที่ 5 แต่โดยรวมคนไทยไม่คุ้นเคยกับเนยในครัวร้อนมากนัก เพราะวัฒนธรรมอาหารเรามักใช้ไขมันจากสัตว์ท้องถิ่นมากกว่า เช่น น้ำมันหมู ไขมันวัว หรือน้ำมันจากไก่และเป็ด
การใช้เนยจึงเป็นเหมือนการสื่อสารข้ามวัฒนธรรม เป็นของเรียบง่ายที่เล่าเรื่องความรู้ของมนุษย์กับธรรมชาติได้อย่างลึกซึ้ง ยิ่งเมื่อเรากลับมานึกถึงภูมิปัญญาเดิม ๆ ก็จะเห็นว่า เนยไม่ได้แค่ให้พลังงาน แต่มันคือไขมันที่พาคุณค่าสารอาหารซึมลึกเข้าไปถึงทุกเนื้อเยื่อ และพาเราเดินทางกลับไปสู่วิถีของอาหารจริง (real food) อย่างสง่างามเลยล่ะ
มาถึงตรงนี้สามารถสรุปง่ายๆจนเห็นภาพโครงสร้างหลักของเนยแล้วใช่ไหมครับว่า เนย = ไขมัน butter oil + เนื้อนม solid milk + ของเหลวอื่นๆ
หลังจากนี้เราจะมาคุยอีกผลผลิตนึง ที่ทำจากเนยครับ จำสมการข้างบนไว้ให้ดีครับ
สำหรับคนที่เพิ่งเริ่มเข้าวงการเนย ตัวนี้เป็น starter ที่ดีครับ วัวกินหญ้า https://s.shopee.co.th/30bQI86d1Q
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ e3ba5e1a:5e433365
2025-02-13 06:16:49
@ e3ba5e1a:5e433365
2025-02-13 06:16:49My favorite line in any Marvel movie ever is in “Captain America.” After Captain America launches seemingly a hopeless assault on Red Skull’s base and is captured, we get this line:
“Arrogance may not be a uniquely American trait, but I must say, you do it better than anyone.”
Yesterday, I came across a comment on the song Devil Went Down to Georgia that had a very similar feel to it:

America has seemingly always been arrogant, in a uniquely American way. Manifest Destiny, for instance. The rest of the world is aware of this arrogance, and mocks Americans for it. A central point in modern US politics is the deriding of racist, nationalist, supremacist Americans.
That’s not what I see. I see American Arrogance as not only a beautiful statement about what it means to be American. I see it as an ode to the greatness of humanity in its purest form.
For most countries, saying “our nation is the greatest” is, in fact, twinged with some level of racism. I still don’t have a problem with it. Every group of people should be allowed to feel pride in their accomplishments. The destruction of the human spirit since the end of World War 2, where greatness has become a sin and weakness a virtue, has crushed the ability of people worldwide to strive for excellence.
But I digress. The fears of racism and nationalism at least have a grain of truth when applied to other nations on the planet. But not to America.
That’s because the definition of America, and the prototype of an American, has nothing to do with race. The definition of Americanism is freedom. The founding of America is based purely on liberty. On the God-given rights of every person to live life the way they see fit.
American Arrogance is not a statement of racial superiority. It’s barely a statement of national superiority (though it absolutely is). To me, when an American comments on the greatness of America, it’s a statement about freedom. Freedom will always unlock the greatness inherent in any group of people. Americans are definitionally better than everyone else, because Americans are freer than everyone else. (Or, at least, that’s how it should be.)
In Devil Went Down to Georgia, Johnny is approached by the devil himself. He is challenged to a ridiculously lopsided bet: a golden fiddle versus his immortal soul. He acknowledges the sin in accepting such a proposal. And yet he says, “God, I know you told me not to do this. But I can’t stand the affront to my honor. I am the greatest. The devil has nothing on me. So God, I’m gonna sin, but I’m also gonna win.”
Libertas magnitudo est
-
 @ eab58da0:eebdafbf
2025-05-14 06:02:17
@ eab58da0:eebdafbf
2025-05-14 06:02:17By Unknownfx
Mental health isn’t just about big breakthroughs; it’s about small, intentional choices that pull you out of your head and into your life. I’ve spent years wrestling with overthinking, chasing perfection, and letting my phone hijack my focus. Here’s what I’ve learned about stopping those cycles and finding peace—and how you can, too.
Trapped in My Own Mind: The Overthinking Struggle I used to overanalyze everything—every word in a conversation, every choice I made. My brain was a hamster wheel, spinning with “what ifs” and worst-case scenarios. It stole my energy and joy. Then, I tried something simple: the 5-4-3-2-1 grounding technique. Name five things you see, four you hear, three you feel, two you smell, one you taste. It sounds basic, but it yanked me out of my head and into the present. Another trick? I set a 10-minute timer to journal my worries, then closed the notebook. That act of “parking” my thoughts gave me permission to move on. Overthinking still creeps in, but these tools help me hit pause and start living.
Letting Go of Perfection to Find Happiness For years, I thought happiness meant getting everything right—perfect work, perfect routines, perfect me. Spoiler: it’s exhausting. One day, I bombed a project and expected to spiral. Instead, I felt… free. I realized perfection was a trap, keeping me from real joy. Now, I aim for “good enough” and celebrate small wins, like finishing a rough draft or just showing up on a tough day. Letting go of flawless opened the door to happiness rooted in progress, not pressure. It’s messy, but it’s honest—and that’s where the good stuff lives.
The No-Phone Hour: A Game-Changer for My Brain My phone was my shadow—scrolling during breakfast, checking notifications mid-thought. It cluttered my mind and fueled my overthinking. So, I started a daily “no-phone hour” in the morning. No screens, just me, a coffee, and quiet. Sometimes I journal, sometimes I stare out the window. At first, it felt weird, like I was missing something. But soon, I noticed my focus sharpening and my stress dipping. That hour became sacred—a reset for my mental health. It’s not about hating tech; it’s about giving your brain space to breathe.
Your Turn to Break Free These shifts—grounding my thoughts, embracing imperfection, and ditching my phone for an hour—haven’t made me “fixed.” They’ve made me freer. They’re small steps, but they add up. Try one this week: maybe a grounding exercise when you’re stuck in your head, or letting a mistake slide without self-criticism. Share your story—what’s one thing you do to quiet your mind or reclaim your focus? Drop it in the comments or post your own note. Let’s learn from each other.
-
 @ daa41bed:88f54153
2025-02-09 16:50:04
@ daa41bed:88f54153
2025-02-09 16:50:04There has been a good bit of discussion on Nostr over the past few days about the merits of zaps as a method of engaging with notes, so after writing a rather lengthy article on the pros of a strategic Bitcoin reserve, I wanted to take some time to chime in on the much more fun topic of digital engagement.
Let's begin by defining a couple of things:
Nostr is a decentralized, censorship-resistance protocol whose current biggest use case is social media (think Twitter/X). Instead of relying on company servers, it relies on relays that anyone can spin up and own their own content. Its use cases are much bigger, though, and this article is hosted on my own relay, using my own Nostr relay as an example.
Zap is a tip or donation denominated in sats (small units of Bitcoin) sent from one user to another. This is generally done directly over the Lightning Network but is increasingly using Cashu tokens. For the sake of this discussion, how you transmit/receive zaps will be irrelevant, so don't worry if you don't know what Lightning or Cashu are.
If we look at how users engage with posts and follows/followers on platforms like Twitter, Facebook, etc., it becomes evident that traditional social media thrives on engagement farming. The more outrageous a post, the more likely it will get a reaction. We see a version of this on more visual social platforms like YouTube and TikTok that use carefully crafted thumbnail images to grab the user's attention to click the video. If you'd like to dive deep into the psychology and science behind social media engagement, let me know, and I'd be happy to follow up with another article.
In this user engagement model, a user is given the option to comment or like the original post, or share it among their followers to increase its signal. They receive no value from engaging with the content aside from the dopamine hit of the original experience or having their comment liked back by whatever influencer they provide value to. Ad revenue flows to the content creator. Clout flows to the content creator. Sales revenue from merch and content placement flows to the content creator. We call this a linear economy -- the idea that resources get created, used up, then thrown away. Users create content and farm as much engagement as possible, then the content is forgotten within a few hours as they move on to the next piece of content to be farmed.
What if there were a simple way to give value back to those who engage with your content? By implementing some value-for-value model -- a circular economy. Enter zaps.

Unlike traditional social media platforms, Nostr does not actively use algorithms to determine what content is popular, nor does it push content created for active user engagement to the top of a user's timeline. Yes, there are "trending" and "most zapped" timelines that users can choose to use as their default, but these use relatively straightforward engagement metrics to rank posts for these timelines.
That is not to say that we may not see clients actively seeking to refine timeline algorithms for specific metrics. Still, the beauty of having an open protocol with media that is controlled solely by its users is that users who begin to see their timeline gamed towards specific algorithms can choose to move to another client, and for those who are more tech-savvy, they can opt to run their own relays or create their own clients with personalized algorithms and web of trust scoring systems.
Zaps enable the means to create a new type of social media economy in which creators can earn for creating content and users can earn by actively engaging with it. Like and reposting content is relatively frictionless and costs nothing but a simple button tap. Zaps provide active engagement because they signal to your followers and those of the content creator that this post has genuine value, quite literally in the form of money—sats.

I have seen some comments on Nostr claiming that removing likes and reactions is for wealthy people who can afford to send zaps and that the majority of people in the US and around the world do not have the time or money to zap because they have better things to spend their money like feeding their families and paying their bills. While at face value, these may seem like valid arguments, they, unfortunately, represent the brainwashed, defeatist attitude that our current economic (and, by extension, social media) systems aim to instill in all of us to continue extracting value from our lives.
Imagine now, if those people dedicating their own time (time = money) to mine pity points on social media would instead spend that time with genuine value creation by posting content that is meaningful to cultural discussions. Imagine if, instead of complaining that their posts get no zaps and going on a tirade about how much of a victim they are, they would empower themselves to take control of their content and give value back to the world; where would that leave us? How much value could be created on a nascent platform such as Nostr, and how quickly could it overtake other platforms?
Other users argue about user experience and that additional friction (i.e., zaps) leads to lower engagement, as proven by decades of studies on user interaction. While the added friction may turn some users away, does that necessarily provide less value? I argue quite the opposite. You haven't made a few sats from zaps with your content? Can't afford to send some sats to a wallet for zapping? How about using the most excellent available resource and spending 10 seconds of your time to leave a comment? Likes and reactions are valueless transactions. Social media's real value derives from providing monetary compensation and actively engaging in a conversation with posts you find interesting or thought-provoking. Remember when humans thrived on conversation and discussion for entertainment instead of simply being an onlooker of someone else's life?
If you've made it this far, my only request is this: try only zapping and commenting as a method of engagement for two weeks. Sure, you may end up liking a post here and there, but be more mindful of how you interact with the world and break yourself from blind instinct. You'll thank me later.

-
 @ ff9ff7e4:a3ba734a
2025-05-14 05:32:22
@ ff9ff7e4:a3ba734a
2025-05-14 05:32:22A 818p se destaca como uma das principais plataformas de entretenimento digital, oferecendo aos jogadores brasileiros uma experiência completa, segura e repleta de emoção. Com um portfólio variado de jogos, navegação intuitiva e suporte dedicado, a 818p tem conquistado um público fiel que busca diversão e praticidade na palma da mão.
Conheça a Plataforma 818p A proposta da 818p é clara: oferecer entretenimento online acessível, confiável e envolvente. Seu site é otimizado tanto para computadores quanto para dispositivos móveis, garantindo uma experiência fluida em qualquer lugar. Logo ao acessar a plataforma, o usuário é recebido com uma interface moderna e organizada, facilitando a navegação entre as seções, como promoções, jogos e suporte.
Outro diferencial importante é o compromisso com a segurança. A 818putiliza tecnologia de ponta para proteger os dados dos jogadores e garantir transações seguras, seja na hora de depositar ou sacar seus ganhos. Além disso, a plataforma segue padrões internacionais de jogo responsável, incentivando uma experiência saudável para todos os usuários.
Jogos para Todos os Estilos Na 818p, há jogos para todos os gostos. Seja você fã de jogos clássicos, competições de sorte ou desafios estratégicos, há sempre algo novo para descobrir.
Entre os destaques estão os jogos de cartas e mesa, muito populares entre os brasileiros. Neles, o jogador encontra versões modernas e interativas de títulos como pôquer, bacará e outros que combinam estratégia com sorte. Os jogos de roleta virtual também fazem sucesso, com gráficos realistas e diversas variações para manter a experiência sempre empolgante.
Outro ponto forte da 818p são os jogos de slots. Com centenas de opções, desde os mais tradicionais até os mais inovadores, os slots da plataforma oferecem gráficos impressionantes, trilhas sonoras imersivas e bônus que aumentam as chances de ganhar. É possível escolher entre temáticas variadas, como mitologia, aventura, filmes e fantasia.
Além disso, a 818p frequentemente atualiza seu catálogo, trazendo novos títulos desenvolvidos por provedores renomados do mercado internacional, garantindo qualidade e inovação constante.
A Experiência do Jogador A satisfação dos jogadores é uma prioridade na 818p. A plataforma oferece um ambiente acolhedor e interativo, com recursos que tornam a experiência ainda mais completa. O processo de cadastro é simples e rápido, permitindo que novos usuários comecem a jogar em poucos minutos.
O suporte ao cliente é outro ponto de destaque. Disponível em português e com atendimento eficiente, a equipe está sempre pronta para ajudar em qualquer dúvida ou problema, seja por chat ao vivo ou e-mail.
Promoções e bônus exclusivos também fazem parte da rotina da 818p. Os jogadores ativos são recompensados com giros grátis, créditos extras e outras vantagens que tornam a jornada ainda mais divertida e vantajosa.
Conclusão A 818p prova que é possível reunir diversão, variedade e segurança em um só lugar. Com uma plataforma moderna, uma seleção impressionante de jogos e um atendimento dedicado, ela se consolida como uma excelente escolha para quem busca entretenimento online de qualidade.
Se você procura uma nova maneira de se divertir e ainda ter a chance de ganhar recompensas, a 818p é a escolha certa. Cadastre-se, explore os jogos disponíveis e descubra por que tantos brasileiros já se tornaram fãs da plataforma!
-
 @ e3ba5e1a:5e433365
2025-02-05 17:47:16
@ e3ba5e1a:5e433365
2025-02-05 17:47:16I got into a friendly discussion on X regarding health insurance. The specific question was how to deal with health insurance companies (presumably unfairly) denying claims? My answer, as usual: get government out of it!
The US healthcare system is essentially the worst of both worlds:
- Unlike full single payer, individuals incur high costs
- Unlike a true free market, regulation causes increases in costs and decreases competition among insurers
I'm firmly on the side of moving towards the free market. (And I say that as someone living under a single payer system now.) Here's what I would do:
- Get rid of tax incentives that make health insurance tied to your employer, giving individuals back proper freedom of choice.
- Reduce regulations significantly.
-
In the short term, some people will still get rejected claims and other obnoxious behavior from insurance companies. We address that in two ways:
- Due to reduced regulations, new insurance companies will be able to enter the market offering more reliable coverage and better rates, and people will flock to them because they have the freedom to make their own choices.
- Sue the asses off of companies that reject claims unfairly. And ideally, as one of the few legitimate roles of government in all this, institute new laws that limit the ability of fine print to allow insurers to escape their responsibilities. (I'm hesitant that the latter will happen due to the incestuous relationship between Congress/regulators and insurers, but I can hope.)
Will this magically fix everything overnight like politicians normally promise? No. But it will allow the market to return to a healthy state. And I don't think it will take long (order of magnitude: 5-10 years) for it to come together, but that's just speculation.
And since there's a high correlation between those who believe government can fix problems by taking more control and demanding that only credentialed experts weigh in on a topic (both points I strongly disagree with BTW): I'm a trained actuary and worked in the insurance industry, and have directly seen how government regulation reduces competition, raises prices, and harms consumers.
And my final point: I don't think any prior art would be a good comparison for deregulation in the US, it's such a different market than any other country in the world for so many reasons that lessons wouldn't really translate. Nonetheless, I asked Grok for some empirical data on this, and at best the results of deregulation could be called "mixed," but likely more accurately "uncertain, confused, and subject to whatever interpretation anyone wants to apply."
https://x.com/i/grok/share/Zc8yOdrN8lS275hXJ92uwq98M
-
 @ ff9ff7e4:a3ba734a
2025-05-14 05:31:49
@ ff9ff7e4:a3ba734a
2025-05-14 05:31:49Nos últimos anos, o entretenimento digital ganhou grande destaque entre os brasileiros, especialmente com o avanço da tecnologia e o fácil acesso à internet. Nesse cenário, a plataforma 133BR surge como uma das grandes promessas do setor, oferecendo uma experiência completa, segura e empolgante para quem busca diversão e recompensas. Seja você um jogador iniciante ou experiente, a 133BR tem muito a oferecer.
Plataforma Moderna e Acessível A 133BR se destaca pela sua interface intuitiva e design moderno, desenvolvido para proporcionar navegação rápida e prática. Desde o momento do cadastro, o usuário é guiado de maneira clara e objetiva, com menus organizados e acesso facilitado a todos os recursos disponíveis.
Além disso, a compatibilidade com diversos dispositivos — incluindo smartphones, tablets e computadores — garante que os jogadores possam se divertir a qualquer hora e em qualquer lugar. Tudo isso com tecnologia de ponta, que assegura estabilidade e fluidez durante o uso.
Diversidade de Jogos para Todos os Gostos Um dos grandes atrativos da 133bré a variedade de jogos oferecidos na plataforma. Com opções que vão desde os clássicos jogos de mesa até os lançamentos mais modernos e interativos, o usuário encontra sempre algo novo para explorar.
Entre os destaques estão:
Jogos de cartas: opções como pôquer, blackjack e outros estilos populares, ideais para quem gosta de usar estratégia e raciocínio.
Roletas interativas: jogos envolventes que misturam sorte com emoção, oferecendo uma experiência dinâmica e imprevisível.
Slots virtuais: com temáticas variadas e gráficos envolventes, os slots da 133BR são perfeitos para quem busca jogabilidade simples, porém empolgante.
Títulos ao vivo: interações em tempo real com apresentadores e outros jogadores, elevando o nível de imersão da plataforma.
Essa diversidade garante que todos os tipos de jogadores — dos mais estratégicos aos mais casuais — encontrem opções que combinem com seu perfil.
Experiência do Jogador: Confiabilidade e Recompensas Outro ponto forte da 133BR é a experiência do usuário como um todo. A plataforma preza pela segurança em todos os processos, desde o cadastro até as transações financeiras. Com métodos de pagamento variados e suporte eficiente, os jogadores podem realizar saques e depósitos com agilidade e tranquilidade.
A 133BR também investe em programas de recompensas e bônus promocionais, que valorizam tanto os novos usuários quanto os veteranos. Essas vantagens aumentam as chances de ganhos e incentivam a permanência dos jogadores na plataforma.
Além disso, o suporte ao cliente é um diferencial. Com atendimento rápido e em português, a equipe está sempre pronta para resolver dúvidas e oferecer suporte técnico, garantindo uma experiência fluida e sem frustrações.
Conclusão A 133BR é uma plataforma completa para quem busca entretenimento online de qualidade. Com um catálogo variado de jogos, ambiente seguro, interface moderna e suporte de excelência, ela se posiciona como uma das principais escolhas entre os brasileiros apaixonados por diversão digital. Se você está em busca de emoção, praticidade e a chance de conquistar grandes prêmios, a 133BR é o destino certo.
-
 @ 65498509:73b0f27f
2025-05-15 00:30:36
@ 65498509:73b0f27f
2025-05-15 00:30:36A
- AdAway
- AIMP
- amnezia-client - Android 7
- amnezia-client - Android 8+
- Ampersand (CI)
- Android System WebView by Cromite - Cromite (arm64)
- Android System WebView by Cromite - Cromite (x64)
- Android System WebView by Thorium - Thorium
- Another Widget
- Anytype - arm v8a
- Anytype - armeabi v7a
- Anytype - universal
- AppVerifier
- Arcticons
- Arcticons Black
- Arcticons Day & Night
- Arcticons Material You
- Aurora Store
- Aurora Store Nightly
- Aves
B
- Bitwarden
- Blitz: Fischer Chess Clock
- Brave
- Brave (Beta)
- Brave (Nightly)
- Breakout 71
- Breezy Weather - Standard Flavour
- Breezy Weather (Freenet) - Freenet Flavour
- Bunny Manager
- Bunny Media Editor - arm
- Bunny Media Editor - arm64-v8a
- Bunny Media Editor - x86
- Bunny Media Editor - x86_64
C
- Chance
- Cheogram
- Citra
- Citra MMJ
- Citra-Enhanced
- citron - Canary Refresh_optimised
- citron - Canary Refresh_release
- Clock - Debug
- Clock - Release
- Collabora Office - arm64 v8a (release version)
- Collabora Office - armeabi v7a (release version)
- Collabora Office - x86 (release version)
- Collabora Office - x86_64 (release version)
- Collabora Office (Snapshot) - arm64 v8a (snapshot version)
- Collabora Office (Snapshot) - armeabi v7a (snapshot version)
- Collabora Office (Snapshot) - x86 (snapshot version)
- Collabora Office (Snapshot) - x86_64 (snapshot version)
- Cromite - arm
- Cromite - arm64
- Cromite - x64
- Cryptomator
- Cube ACR
- Cwtch - Cwtch-Website
- cwtch-ui - OpenPrivacy-Forgejo (Cwtch-Repo)
D
- Delta - release
- Delta - beta
- Delta (foss) - foss beta
- Delta (foss) - foss release
- Dolphin |MMJR2| VBI
- Dolphin Emulator (Nightly)
- Droidsound-E
- DS Audio - cn
- DS Audio - ww
- DuckStation - Preview/Beta
- DuckStation - Stable
- Duolingo Revanced
E
- Electrum - arm64-v8a
- Electrum - armeabi-v7a
- Electrum - x86_64
- Element
- Ente Auth
- Ente Photos
- EpicGames Store
- EVMap
- Exodus
F
- FairEmail
- Firefox - arm64 v8a
- Firefox - armeabi v7a
- Firefox - x86
- Firefox - x86_64
- Firefox Beta - arm64 v8a
- Firefox Beta - armeabi v7a
- Firefox Beta - universal
- Firefox Beta - x86
- Firefox Beta - x86_64
- Firefox Focus (stable) - arm64 v8a
- Firefox Klar (stable) - arm64 v8a
- Firefox Nightly for Developers - arm64 v8a
- Firefox Nightly for Developers - armeabi v7a
- Firefox Nightly for Developers - universal
- Firefox Nightly for Developers - x86
- Firefox Nightly for Developers - x86_64
- floccus bookmark sync
- FlorisBoard Preview
- FlorisBoard Stable
G
- GeoGebra - 5.2
- GNU Emacs - arm64-v8a, API level 21
- GNU Emacs - arm64-v8a, API level 29
- GNU Emacs - armeabi-v7a, API level 16
- GNU Emacs - armeabi-v7a, API level 24
- GNU Emacs - armeabi, API level 8
- GNU Emacs - armeabi, API level 9
- GNU Emacs - mips, API level 9
- GNU Emacs - mips64, API level 21
- GNU Emacs - x86_64, API level 21
- GNU Emacs - x86_64, API level 29
- GNU Emacs - x86, API level 9
- Grayjay
H
- HeliBoard - Debug
- HeliBoard - normal
- HeliBoard - nouserlib
- Hermit – Lite Apps Browser
- Home Assistant
- HSBC HK
I
- Image Toolbox
- Imagepipe
- Infinity
- InviZible Beta - arm64
- InviZible Beta - universal
- InviZible Lite - arm64
- InviZible Lite - universal
- IronFox - GitLab
- IronFox - IronFox OSS's F-Droid Repo
J
K
L
M
- MacroDroid - arm64 v8a
- MacroDroid - universal
- MacroDroid Helper - android 13-
- MacroDroid Helper - android 14+ (track only)
- Markor
- Mastodon
- Material Files
- Mattermost
- melonDS
- melonDS Nightly
- MiXplorer (Beta) - arm
- MiXplorer (Beta) - arm64
- MiXplorer (Beta) - x64
- MiXplorer (Beta) - x86
- Molly
- Monero.com
- MT Manager - clone
- MT Manager - clone (sdk28)
- MT Manager - normal
- MT Manager - normal (sdk28)
- Mullvad VPN
- MuPDF viewer
N
- NewPipe
- News
- Nextcloud Talk - GitHub
- Nextcloud Talk - gplay
- Nova Launcher (Beta))
- Nova Launcher stable - stable (official))
- Nova Launcher stable - stable (revanced)
- ntfy
O
- Obsidian
- Obtainium - GitHub (F-Droid variant)
- Open Camera
- Orbot - arm64v8-stable
- Orbot (Beta) - arm64v8-beta
- OsmAnd
- OSS Card Wallet
- OSS Document Scanner
P
- Paperless Mobile
- PeerTube
- personalDNSfilter - f-droid.org
- personalDNSfilter - www.zenz-solutions.de
- Play!
- PPSSPP
- PPSSPP VR
- Privacy Cell
- ProseReader (Optimum)
- Proton Calendar
- Proton Drive
- Proton Pass
Q
R
- RAR
- Read You
- Reddit - beta (revanced extended)
- Reddit - beta (revanced)
- Reddit - stable (revanced extended)
- Reddit - stable (revanced)
- RedReader
- RetroArch (32-bit) - Nightly
- RetroArch (32-bit) - Stable
- RetroArch (AArch64) - Nightly
- RetroArch (AArch64) - Stable
- RetroArch (Universal) - Nightly
- RetroArch (Universal) - Stable
- Revanced Adobe Lightroom - beta (universal)
- Revanced Adobe Lightroom - stable (universal)
- Revanced Facebook - beta (arm64-v8a)
- Revanced Facebook - stable (arm64-v8a)
- Revanced Facebook Messenger - beta (arm64-v8a)
- Revanced Facebook Messenger - stable (arm64-v8a)
- Revanced Facebook Messenger - stable (armeabi-v7a)
- Revanced Instagram - beta (arm64-v8a)
- Revanced Instagram - stable (arm64-v8a)
- Revanced Instagram - stable (armeabi-v7a)
- ReVanced microG Services
- Revanced Pixiv - beta (universal)
- Revanced Pixiv - stable (universal)
- Revanced YouTube - revanced (arm64 v8a; Android 7+)
S
- SchildiChat - FOSS-Push Stable (F-Droid)
- SchildiChat - Google FCM-Push (SpiritCroc)
- SchildiChat.Beta[f] - FOSS-Push Beta (SpiritCroc)
- SchildiChat.Beta[g] - Google Play Store Beta (SpiritCroc)
- SchildiChat[f] - FOSS-Push Stable (SpiritCroc)
- SchildiChat[g] - Google Play Store Stable (SpiritCroc)
- ScummVM
- SD Maid SE
- Shelter - PeterCxy's F-Droid Repo
- Shizuku
- Signal
- SM64 Builder
- Sonic 3 A.I.R.
- Sonic Robo Blast 2
- Steam
- Steam Chat
- Steam Link
- Stremio
- Syncthing-Fork
- Synology Active Insight - cn
- Synology Active Insight - ww
- Synology Bee Drive - cn
- Synology Bee Drive - ww
- Synology Bee Photos - cn
- Synology Bee Photos - ww
- Synology Bee Station Drive - cn
- Synology Bee Station Drive - ww
- Synology Drive - cn
- Synology Drive - ww
- Synology Photos - cn
- Synology Photos - ww
T
- Tasks
- Telegram
- termux-boot
- Termux:API
- Termux:Widget
- Thorium-Android
- Thorium-Shell
- Thunderbird
- Thunderbird Beta
- Thunderbird Nightly
- Tor Browser
- Total Commander
- Totalcmd-Drive
- TotalCmd-FTP (File Transfers)
- TotalCmd-LAN (Windows shares)
- TotalCmd-SFTP
- TotalCmd-WebDAV (WEB Folders)
- TotalCmd-Wifi Transfer
- Totalcmd-Windows Live OneDrive
- Transistor
- Turrit
- Tuta
U
V
- Vespucci
- Vita3K
- Vivaldi - arm64-v8a
- Vivaldi - armeabi-v7a
- Vivaldi - x86-64
- Vivaldi Snapshot - arm64-v8a
- Vivaldi Snapshot - armeabi-v7a
- Vivaldi Snapshot - x86-64
- VLC - arm64-v8a
- VLC - armeabi-v7a
- VLC - x86_64
W
X
Z
-
 @ 91bea5cd:1df4451c
2025-02-04 17:24:50
@ 91bea5cd:1df4451c
2025-02-04 17:24:50Definição de ULID:
Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível.
Gerar ULID
```sql
CREATE EXTENSION IF NOT EXISTS pgcrypto;
CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\000\000\000\000\000\000'; output TEXT = '';
unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER);
-- 10 entropy bytes ulid = timestamp || gen_random_bytes(10);
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ```
ULID TO UUID
```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF;
v = regexp_split_to_array(ulid, '');
-- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]);
-- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]);
RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE;
CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ```
UUID to ULID
```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ```
Gera 11 Digitos aleatórios: YBKXG0CKTH4
```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto;
-- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT;
-- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars;END; $$ LANGUAGE plpgsql; ```
Exemplo de USO
```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL );
-- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ```
Fontes
- https://github.com/scoville/pgsql-ulid
- https://github.com/geckoboard/pgulid
-
 @ 91bea5cd:1df4451c
2025-02-04 17:15:57
@ 91bea5cd:1df4451c
2025-02-04 17:15:57Definição de ULID:
Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível.
Gerar ULID
```sql
CREATE EXTENSION IF NOT EXISTS pgcrypto;
CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\000\000\000\000\000\000'; output TEXT = '';
unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER);
-- 10 entropy bytes ulid = timestamp || gen_random_bytes(10);
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ```
ULID TO UUID
```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF;
v = regexp_split_to_array(ulid, '');
-- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]);
-- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]);
RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE;
CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ```
UUID to ULID
```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ```
Gera 11 Digitos aleatórios: YBKXG0CKTH4
```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto;
-- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT;
-- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars;END; $$ LANGUAGE plpgsql; ```
Exemplo de USO
```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL );
-- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ```
Fontes
- https://github.com/scoville/pgsql-ulid
- https://github.com/geckoboard/pgulid
-
 @ 9c9d2765:16f8c2c2
2025-05-14 05:23:35
@ 9c9d2765:16f8c2c2
2025-05-14 05:23:35CHAPTER EIGHTEEN
"I’ve got something you’ll love. A woman, probably James’s sister from the street, came begging for money at JP today. He humiliated her. The whole thing happened in front of staff. Check the photos attached. This could ruin him if we spin it well."
Within minutes, Helen replied: “Excellent. This might be the leverage we’ve been waiting for. Keep digging, Tracy. He can’t escape the past forever.”
Mark responded too, bitter laughter echoing in his voice note: “The mighty always fall. This is just the beginning.”
But what none of them knew was that James had already noticed Tracy's growing interest in him, her subtle spying, her conveniently timed questions, and now this bold move to document his personal confrontation. He wasn’t going to act just yet… but he was watching.
"Have you seen the news?" Sandra’s voice crackled through the phone, her tone urgent and unsettled.
James, seated in his office at JP Enterprises, furrowed his brows. He hadn’t turned on the television yet. "No. What happened?"
"You need to check the headlines immediately. It’s everywhere. They’ve dragged your name through the mud!"
Without another word, James reached for the remote and turned on the large flat-screen mounted on his office wall. The screen lit up with a news report, the broadcaster’s voice sharp and sensational.
“Shocking footage surfaces: JP Enterprises’ President humiliates his only sister in broad daylight!”
Photos of James and Evelyn outside the company played in a dramatic sequence him confronting her, her being escorted out, and his seemingly cold expression. The captions twisted the story:
“Heartless Billionaire?” “President throws out helpless sister for asking money” “The shameful side of JP Enterprises’ leader exposed!”
James leaned back in his chair, eyes narrowing as he watched.
"This is calculated," he muttered under his breath. "Scripted. Twisted."
He turned off the screen and called Sandra back. "I want Tracy's devices checked. Every message, every image. And I want a full trace on the origin of this story. Media outlets don’t run this kind of narrative without a source."
"You think Tracy’s behind it?" Sandra asked, her voice low.
"She took the pictures, I’m sure of it. But she’s not working alone," James replied, voice steely. "This is too well-planned for one person. They’re trying to frame me, twist reality, and attack my image. And I’ll make sure every single one of them is exposed."
Meanwhile, at a discreet location, Mark, Helen, and Tracy gathered to watch the fire they had ignited. Tracy grinned as she scrolled through social media posts and reactions.
"It’s gone viral," she said gleefully. "Everyone thinks that woman’s your sister. It’s everywhere on blogs, gossip pages, even official news networks. The damage is done."
Mark chuckled darkly. "This will shatter his reputation. Let’s see how he enjoys being publicly hated."
Helen, sipping her wine with a satisfied look, added, "It’s only the beginning. Let’s push this narrative harder. We’ll make sure the board at JP Enterprises starts questioning his character."
But little did they know James had already activated his private investigative team. Every file, every message, every trail was being traced.
Back at JP Enterprises, James stood by the window of his office, watching the skyline, his hands in his pockets.
"They want a war?" he said to himself quietly. "Then I’ll give them one. But on my own terms."
His phone buzzed. A message from his chief of cyber-security read:
“We’ve located the media contact. Payment traced to a dummy account linked to Helen Ray.”
James stared at the screen, his jaw tightening.
The day of the much-anticipated 16th Anniversary of JP Enterprises finally arrived, cloaked in glamour, prestige, and tension. The event venue, a grand luxury hall draped in velvet and golden decor, radiated elegance and opulence. Bright lights illuminated the red carpet, and camera flashes sparked like lightning as influential business magnates, city officials, and esteemed guests from far and wide began to pour in.
Among the prominent guests were Helen Ray, Mark, Tracy, and other members of the Ray family. Dressed in designer gowns and tailored suits, they mingled with high society, laughing and sipping champagne, their polished facades hiding the scheme they had carefully orchestrated for the night.
The hall buzzed with anticipation for the arrival of Mr. and Mrs. JP, the founders of the JP Empire. Meanwhile, in a secluded corner of the hall, Helen leaned towards Mark, whispering with a smirk, “She’s on her way. Get ready for the show.”
The “she” Helen referred to was Evelyn, the same woman they had bribed to once again impersonate James’s sister and stir public humiliation. This time, it wouldn’t just be a few photos, they wanted a scandal of epic proportions, a scene so chaotic and public that it would crumble James’s standing in the business world for good.
As guests chatted and live music flowed through the air, James entered the hall in a pristine black tuxedo, exuding power and poise. He walked beside his uncle Charles and his loyal staff, warmly greeting dignitaries and longtime associates. His presence commanded attention, but murmurs soon rippled through the crowd.
Whispers filled the air like wind in dry grass:
"That’s the man from the headline, isn’t he?" "They say he threw his own sister out for asking for help." "Such cruelty… and yet here he is, smiling like a saint."
As James navigated through the crowd with measured grace, Helen sauntered over, her heels clicking on the marble floor, her expression dripping with sarcasm.
“Well, well, if it isn’t our gallant President,” she began, feigning admiration. “I must say, you clean up well for someone who was just exposed in the most shameful news of the year.”
James turned to her with a calm but unreadable gaze. “Helen,” he greeted curtly.
She chuckled. “You really should be more careful with family matters. The public has a long memory, you know.”
Before James could reply, a loud voice broke through the soft music. “James! James! You left me with nothing!”
All heads turned toward the entrance, where Evelyn stumbled in, her appearance carefully staged to look disheveled and distraught. She weaved through the crowd, screaming and sobbing uncontrollably, clutching at the air as security hesitated to intervene.
-
 @ e3ba5e1a:5e433365
2025-02-04 08:29:00
@ e3ba5e1a:5e433365
2025-02-04 08:29:00President Trump has started rolling out his tariffs, something I blogged about in November. People are talking about these tariffs a lot right now, with many people (correctly) commenting on how consumers will end up with higher prices as a result of these tariffs. While that part is true, I’ve seen a lot of people taking it to the next, incorrect step: that consumers will pay the entirety of the tax. I put up a poll on X to see what people thought, and while the right answer got a lot of votes, it wasn't the winner.

For purposes of this blog post, our ultimate question will be the following:
- Suppose apples currently sell for $1 each in the entire United States.
- There are domestic sellers and foreign sellers of apples, all receiving the same price.
- There are no taxes or tariffs on the purchase of apples.
- The question is: if the US federal government puts a $0.50 import tariff per apple, what will be the change in the following:
- Number of apples bought in the US
- Price paid by buyers for apples in the US
- Post-tax price received by domestic apple producers
- Post-tax price received by foreign apple producers
Before we can answer that question, we need to ask an easier, first question: before instituting the tariff, why do apples cost $1?
And finally, before we dive into the details, let me provide you with the answers to the ultimate question. I recommend you try to guess these answers before reading this, and if you get it wrong, try to understand why:
- The number of apples bought will go down
- The buyers will pay more for each apple they buy, but not the full amount of the tariff
- Domestic apple sellers will receive a higher price per apple
- Foreign apple sellers will receive a lower price per apple, but not lowered by the full amount of the tariff
In other words, regardless of who sends the payment to the government, both taxed parties (domestic buyers and foreign sellers) will absorb some of the costs of the tariff, while domestic sellers will benefit from the protectionism provided by tariffs and be able to sell at a higher price per unit.
Marginal benefit
All of the numbers discussed below are part of a helper Google Sheet I put together for this analysis. Also, apologies about the jagged lines in the charts below, I hadn’t realized before starting on this that there are some difficulties with creating supply and demand charts in Google Sheets.
Let’s say I absolutely love apples, they’re my favorite food. How much would I be willing to pay for a single apple? You might say “$1, that’s the price in the supermarket,” and in many ways you’d be right. If I walk into supermarket A, see apples on sale for $50, and know that I can buy them at supermarket B for $1, I’ll almost certainly leave A and go buy at B.
But that’s not what I mean. What I mean is: how high would the price of apples have to go everywhere so that I’d no longer be willing to buy a single apple? This is a purely personal, subjective opinion. It’s impacted by how much money I have available, other expenses I need to cover, and how much I like apples. But let’s say the number is $5.
How much would I be willing to pay for another apple? Maybe another $5. But how much am I willing to pay for the 1,000th apple? 10,000th? At some point, I’ll get sick of apples, or run out of space to keep the apples, or not be able to eat, cook, and otherwise preserve all those apples before they rot.
The point being: I’ll be progressively willing to spend less and less money for each apple. This form of analysis is called marginal benefit: how much benefit (expressed as dollars I’m willing to spend) will I receive from each apple? This is a downward sloping function: for each additional apple I buy (quantity demanded), the price I’m willing to pay goes down. This is what gives my personal demand curve. And if we aggregate demand curves across all market participants (meaning: everyone interested in buying apples), we end up with something like this:
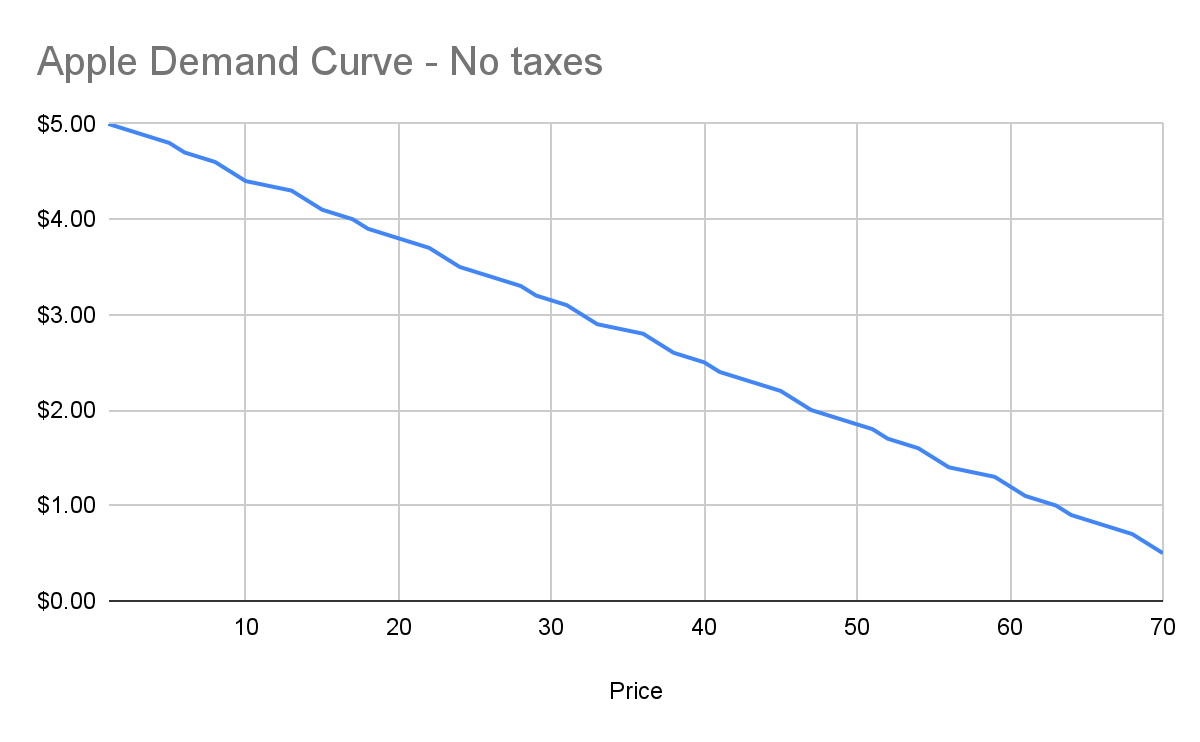
Assuming no changes in people’s behavior and other conditions in the market, this chart tells us how many apples will be purchased by our buyers at each price point between $0.50 and $5. And ceteris paribus (all else being equal), this will continue to be the demand curve for apples.
Marginal cost
Demand is half the story of economics. The other half is supply, or: how many apples will I sell at each price point? Supply curves are upward sloping: the higher the price, the more a person or company is willing and able to sell a product.
Let’s understand why. Suppose I have an apple orchard. It’s a large property right next to my house. With about 2 minutes of effort, I can walk out of my house, find the nearest tree, pick 5 apples off the tree, and call it a day. 5 apples for 2 minutes of effort is pretty good, right?
Yes, there was all the effort necessary to buy the land, and plant the trees, and water them… and a bunch more than I likely can’t even guess at. We’re going to ignore all of that for our analysis, because for short-term supply-and-demand movement, we can ignore these kinds of sunk costs. One other simplification: in reality, supply curves often start descending before ascending. This accounts for achieving efficiencies of scale after the first number of units purchased. But since both these topics are unneeded for understanding taxes, I won’t go any further.
Anyway, back to my apple orchard. If someone offers me $0.50 per apple, I can do 2 minutes of effort and get $2.50 in revenue, which equates to a $75/hour wage for me. I’m more than happy to pick apples at that price!
However, let’s say someone comes to buy 10,000 apples from me instead. I no longer just walk out to my nearest tree. I’m going to need to get in my truck, drive around, spend the day in the sun, pay for gas, take a day off of my day job (let’s say it pays me $70/hour). The costs go up significantly. Let’s say it takes 5 days to harvest all those apples myself, it costs me $100 in fuel and other expenses, and I lose out on my $70/hour job for 5 days. We end up with:
- Total expenditure: $100 + $70 * 8 hours a day * 5 days \== $2900
- Total revenue: $5000 (10,000 apples at $0.50 each)
- Total profit: $2100
So I’m still willing to sell the apples at this price, but it’s not as attractive as before. And as the number of apples purchased goes up, my costs keep increasing. I’ll need to spend more money on fuel to travel more of my property. At some point I won’t be able to do the work myself anymore, so I’ll need to pay others to work on the farm, and they’ll be slower at picking apples than me (less familiar with the property, less direct motivation, etc.). The point being: at some point, the number of apples can go high enough that the $0.50 price point no longer makes me any money.
This kind of analysis is called marginal cost. It refers to the additional amount of expenditure a seller has to spend in order to produce each additional unit of the good. Marginal costs go up as quantity sold goes up. And like demand curves, if you aggregate this data across all sellers, you get a supply curve like this:
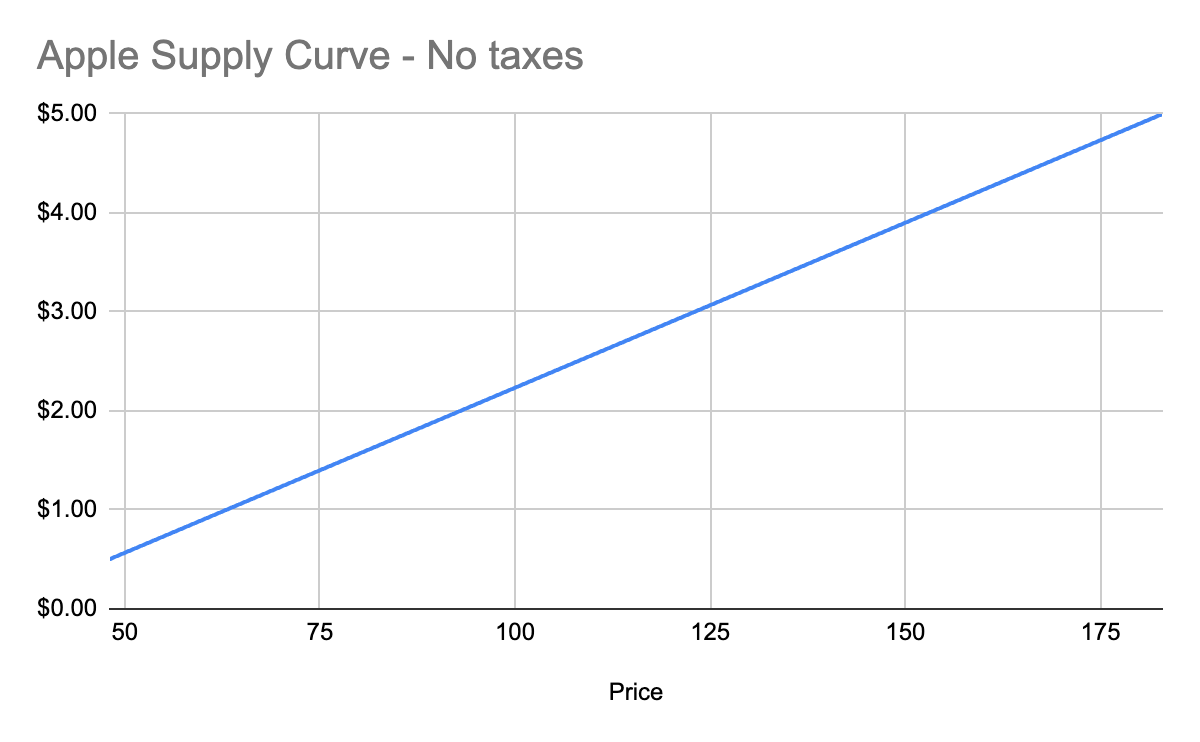
Equilibrium price
We now know, for every price point, how many apples buyers will purchase, and how many apples sellers will sell. Now we find the equilibrium: where the supply and demand curves meet. This point represents where the marginal benefit a buyer would receive from the next buyer would be less than the cost it would take the next seller to make it. Let’s see it in a chart:
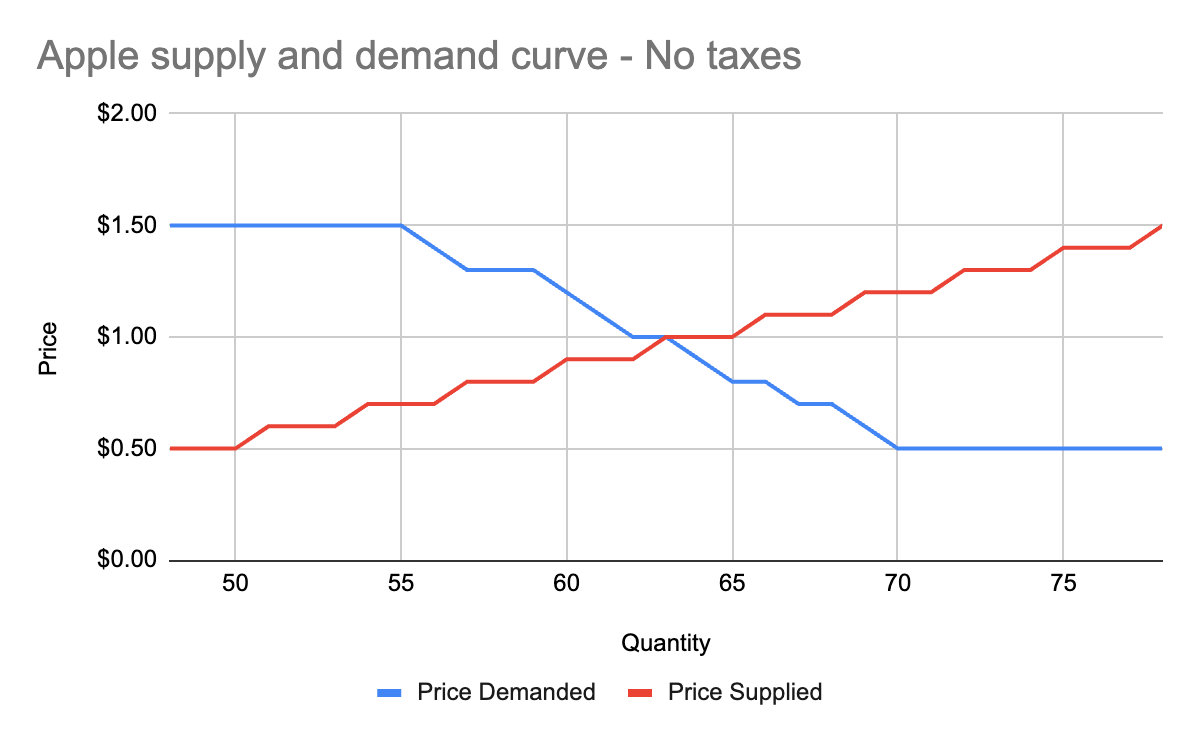
You’ll notice that these two graphs cross at the $1 price point, where 63 apples are both demanded (bought by consumers) and supplied (sold by producers). This is our equilibrium price. We also have a visualization of the surplus created by these trades. Everything to the left of the equilibrium point and between the supply and demand curves represents surplus: an area where someone is receiving something of more value than they give. For example:
- When I bought my first apple for $1, but I was willing to spend $5, I made $4 of consumer surplus. The consumer portion of the surplus is everything to the left of the equilibrium point, between the supply and demand curves, and above the equilibrium price point.
- When a seller sells his first apple for $1, but it only cost $0.50 to produce it, the seller made $0.50 of producer surplus. The producer portion of the surplus is everything to the left of the equilibrium point, between the supply and demand curves, and below the equilibrium price point.
Another way of thinking of surplus is “every time someone got a better price than they would have been willing to take.”
OK, with this in place, we now have enough information to figure out how to price in the tariff, which we’ll treat as a negative externality.
Modeling taxes
Alright, the government has now instituted a $0.50 tariff on every apple sold within the US by a foreign producer. We can generally model taxes by either increasing the marginal cost of each unit sold (shifting the supply curve up), or by decreasing the marginal benefit of each unit bought (shifting the demand curve down). In this case, since only some of the producers will pay the tax, it makes more sense to modify the supply curve.
First, let’s see what happens to the foreign seller-only supply curve when you add in the tariff:
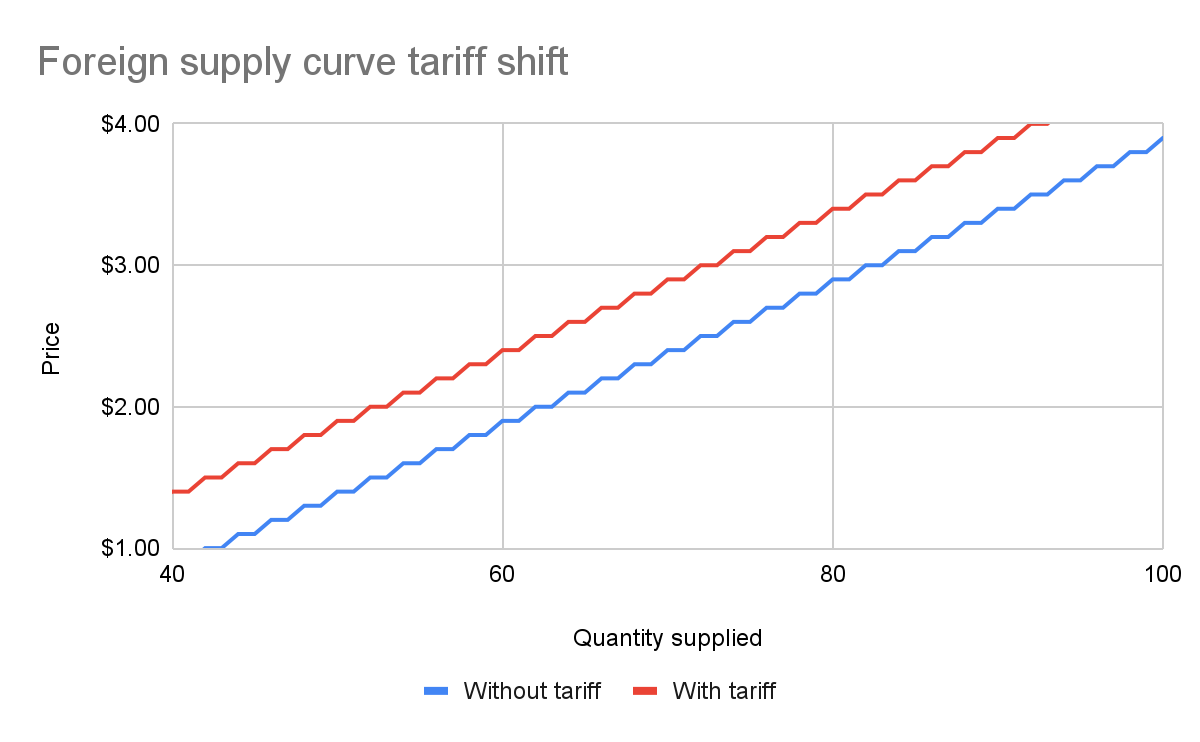
With the tariff in place, for each quantity level, the price at which the seller will sell is $0.50 higher than before the tariff. That makes sense: if I was previously willing to sell my 82nd apple for $3, I would now need to charge $3.50 for that apple to cover the cost of the tariff. We see this as the tariff “pushing up” or “pushing left” the original supply curve.
We can add this new supply curve to our existing (unchanged) supply curve for domestic-only sellers, and we end up with a result like this:
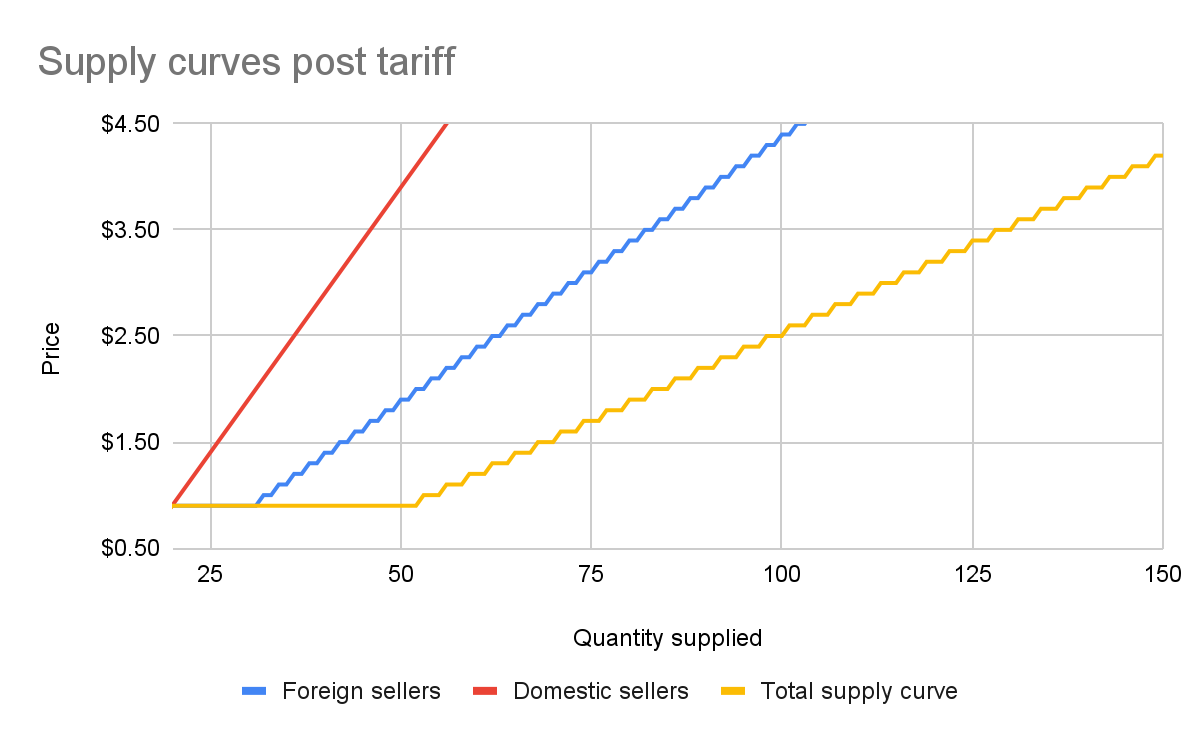
The total supply curve adds up the individual foreign and domestic supply curves. At each price point, we add up the total quantity each group would be willing to sell to determine the total quantity supplied for each price point. Once we have that cumulative supply curve defined, we can produce an updated supply-and-demand chart including the tariff:
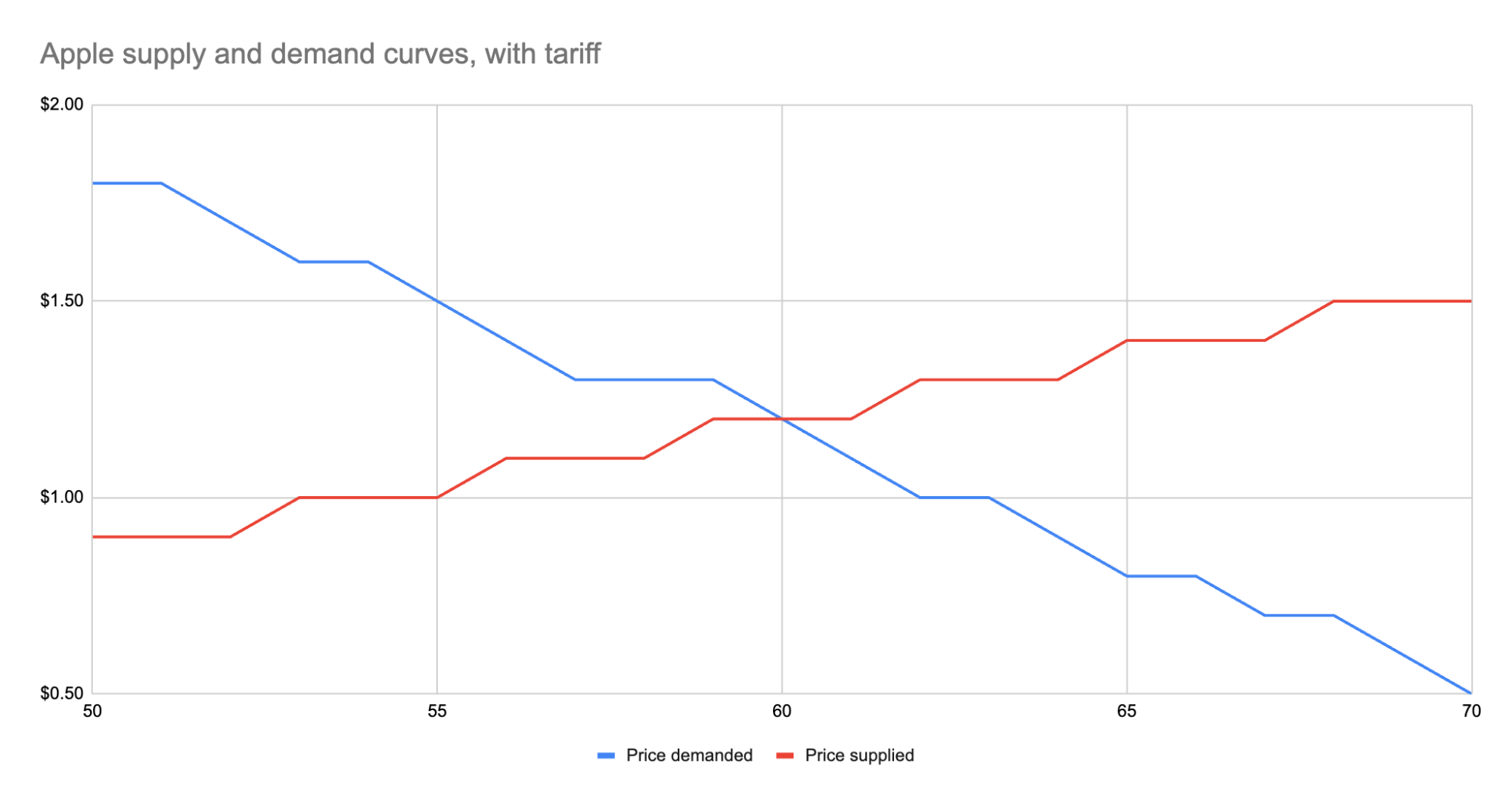
As we can see, the equilibrium has shifted:
- The equilibrium price paid by consumers has risen from $1 to $1.20.
- The total number of apples purchased has dropped from 63 apples to 60 apples.
- Consumers therefore received 3 less apples. They spent $72 for these 60 apples, whereas previously they spent $63 for 3 more apples, a definite decrease in consumer surplus.
- Foreign producers sold 36 of those apples (see the raw data in the linked Google Sheet), for a gross revenue of $43.20. However, they also need to pay the tariff to the US government, which accounts for $18, meaning they only receive $25.20 post-tariff. Previously, they sold 42 apples at $1 each with no tariff to be paid, meaning they took home $42.
- Domestic producers sold the remaining 24 apples at $1.20, giving them a revenue of $28.80. Since they don’t pay the tariff, they take home all of that money. By contrast, previously, they sold 21 apples at $1, for a take-home of $21.
- The government receives $0.50 for each of the 60 apples sold, or in other words receives $30 in revenue it wouldn’t have received otherwise.
We could be more specific about the surpluses, and calculate the actual areas for consumer surplus, producer surplus, inefficiency from the tariff, and government revenue from the tariff. But I won’t bother, as those calculations get slightly more involved. Instead, let’s just look at the aggregate outcomes:
- Consumers were unquestionably hurt. Their price paid went up by $0.20 per apple, and received less apples.
- Foreign producers were also hurt. Their price received went down from the original $1 to the new post-tariff price of $1.20, minus the $0.50 tariff. In other words: foreign producers only receive $0.70 per apple now. This hurt can be mitigated by shifting sales to other countries without a tariff, but the pain will exist regardless.
- Domestic producers scored. They can sell less apples and make more revenue doing it.
- And the government walked away with an extra $30.
Hopefully you now see the answer to the original questions. Importantly, while the government imposed a $0.50 tariff, neither side fully absorbed that cost. Consumers paid a bit more, foreign producers received a bit less. The exact details of how that tariff was split across the groups is mediated by the relevant supply and demand curves of each group. If you want to learn more about this, the relevant search term is “price elasticity,” or how much a group’s quantity supplied or demanded will change based on changes in the price.
Other taxes
Most taxes are some kind of a tax on trade. Tariffs on apples is an obvious one. But the same applies to income tax (taxing the worker for the trade of labor for money) or payroll tax (same thing, just taxing the employer instead). Interestingly, you can use the same model for analyzing things like tax incentives. For example, if the government decided to subsidize domestic apple production by giving the domestic producers a $0.50 bonus for each apple they sell, we would end up with a similar kind of analysis, except instead of the foreign supply curve shifting up, we’d see the domestic supply curve shifting down.
And generally speaking, this is what you’ll always see with government involvement in the economy. It will result in disrupting an existing equilibrium, letting the market readjust to a new equilibrium, and incentivization of some behavior, causing some people to benefit and others to lose out. We saw with the apple tariff, domestic producers and the government benefited while others lost.
You can see the reverse though with tax incentives. If I give a tax incentive of providing a deduction (not paying income tax) for preschool, we would end up with:
- Government needs to make up the difference in tax revenue, either by raising taxes on others or printing more money (leading to inflation). Either way, those paying the tax or those holding government debased currency will pay a price.
- Those people who don’t use the preschool deduction will receive no benefit, so they simply pay a cost.
- Those who do use the preschool deduction will end up paying less on tax+preschool than they would have otherwise.
This analysis is fully amoral. It’s not saying whether providing subsidized preschool is a good thing or not, it simply tells you where the costs will be felt, and points out that such government interference in free economic choice does result in inefficiencies in the system. Once you have that knowledge, you’re more well educated on making a decision about whether the costs of government intervention are worth the benefits.
-
 @ 9e69e420:d12360c2
2025-02-01 11:16:04
@ 9e69e420:d12360c2
2025-02-01 11:16:04Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.

CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language.
One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse.
-
 @ 52524fbb:ae4025dc
2025-05-14 03:14:02
@ 52524fbb:ae4025dc
2025-05-14 03:14:02
The World of Higher Education
Students in the world The nostr ecosystem to university students across the world is like a dream come through in terms of its main feature of decentralisation, which to them is an eye opener from censorship The feeling of having and being free to carry out activities without the fear of being flagged down or zoomed in at, is indeed thrilling and beyond comparison. This Leeds us to one of the most amazing platforms running on the Nostr ecosystem known as Yakihonne, it's impact on decentralisation and bitcoin collaboration with various related communities deserves the name of the fastest growing decentralised media in the world, known for it's article implementation, a large variety of customizable widgets, a friendly user interface and it's lightning fast wallet, this platform known widely for it's phrase of "value -value" is indeed beyond comparison
-
 @ 0fa80bd3:ea7325de
2025-01-30 04:28:30
@ 0fa80bd3:ea7325de
2025-01-30 04:28:30"Degeneration" or "Вырождение" ![[photo_2025-01-29 23.23.15.jpeg]]
A once-functional object, now eroded by time and human intervention, stripped of its original purpose. Layers of presence accumulate—marks, alterations, traces of intent—until the very essence is obscured. Restoration is paradoxical: to reclaim, one must erase. Yet erasure is an impossibility, for to remove these imprints is to deny the existence of those who shaped them.
The work stands as a meditation on entropy, memory, and the irreversible dialogue between creation and decay.
-
 @ 502ab02a:a2860397
2025-05-14 01:02:42
@ 502ab02a:a2860397
2025-05-14 01:02:42เราก็คุยเรื่อง Future Food กันมาสักพักแล้ว หลายคนอาจจะคิดว่ามีการจัดสรรกันลงตัวใช่ไหมครับ ต้องขอโทษด้วย โลกแห่งความเป็นจริงนั้น ผู้ล่าที่แข็งแกร่งถึงจะอยู่รอดเป็นจ่าฝูง (นี่ขนาดผู้ล่านะครับ เหยื่ออย่างเรา อย่าเจ๋อเลยเชียว ฮาๆๆ)
วันนี้เราจะมารู้จักผู้เล่นสนามนี้อีกเจ้านึง ที่เขย่าวงการชีส เช่นกันนั่นคือ Formo ผู้ที่ปฏิวัติวงการชีสด้วยเทคโนโลยี Precision Fermentation อีกเจ้านึงนั่นเองครับ
ถ้าพูดถึงชีส คนส่วนใหญ่มักนึกถึงกลิ่นหอม มัน เค็มละมุนของผลิตภัณฑ์จากนมวัว บางคนกินคู่ไวน์ บางคนโปะบนพิซซ่า หรือบางทีก็แค่ขูดโรยหน้าสลัดให้ดูดีมีระดับขึ้นมาทันตา แต่ในวันที่โลกหมุนไปเร็ว และการเคลื่อนสู่อาหารอนาคต นำทั้งเรื่องการใช้ทรัพยากรจากสัตว์ การปล่อยก๊าซเรือนกระจก และแม้แต่สุขภาพมาเป็นจุดเปลี่ยนของผลประโยชน์ระดับโลก
และนั่นคือจุดที่บริษัทเล็ก ๆ จากเยอรมนีที่ชื่อว่า “Formo” กำลังก้าวเข้ามาเปลี่ยนเกมในโลกของชีส ด้วยเทคโนโลยีที่เรียกว่า “precision fermentation” อีกเช่นกัน เทคโนโลยียอดนิยมที่ในวงการมีในครอบครองมากมายแต่ตลาดผู้บริโภค ยังแทบไม่เคยได้ยินกัน เทคโนโลยีที่ทำให้ไม่ต้องรีดนมหรือเลี้ยงวัวเลยสักตัว แต่ได้ชีสที่กลิ่น เนื้อสัมผัส และโปรตีนเคซีนเหมือนกับชีสจริงเป๊ะ ๆ ราวกับเสกขึ้นมา
Formo ใช้เชื้อราที่ชื่อว่า Aspergillus oryzae หรือที่เรารู้จักกันในชื่อ “โคจิ” ซึ่งมีประวัติการใช้งานยาวนานในอาหารเอเชียอย่างมิโสะ ซอสถั่วเหลือง และสาเก เชื้อนี้ถูกนำมาดัดแปลงพันธุกรรมให้สามารถผลิตโปรตีนเคซีน ซึ่งเป็นโปรตีนหลักในน้ำนมวัว จากนั้นก็เลี้ยงในถังหมัก (bioreactor) ภายใต้การควบคุมอย่างแม่นยำ เพื่อให้เชื้อราทำหน้าที่เป็นโรงงานชีวภาพขนาดจิ๋ว ผลิตโปรตีนออกมาอย่างปลอดภัยและมีประสิทธิภาพ เมื่อนำโปรตีนที่ได้มาผสมกับไขมันและส่วนประกอบอื่น ๆ ก็สามารถสร้างชีสที่ทั้งหน้าตา รสชาติ และเนื้อสัมผัสใกล้เคียงของจริงจนนักชิมสายแข็งยังต้องเลิกคิ้ว ซึ่งทั้งหมดนี้เกิดขึ้นโดยไม่ต้องใช้วัวเลยแม้แต่น้อย ลดการใช้ทรัพยากรธรรมชาติไปมหาศาล และยังหลีกเลี่ยงการใช้ยาปฏิชีวนะ ฮอร์โมน หรือปัจจัยเสี่ยงจากอุตสาหกรรมนมแบบดั้งเดิมอีกด้วย ถ้าไม่มองใส้ในนี่รับรองว่าได้ใจประชากรโลกไปแน่ๆอะครับ
ไม่ใช่แค่ มอสซาเรลลา แต่ชีสจาก Formo มีให้เลือกหลายแบบ ตั้งแต่ “Frischhain” ซึ่งเป็นชีสสเปรดนุ่ม ๆ มีรสสมุนไพรและมะเขือเทศ ไปจนถึง “Camembritz” ชีสนุ่มสไตล์ฝรั่งเศส และ “Cité Bleu” ที่มีกลิ่นแรงแบบบลูชีส เหมาะสำหรับคนที่ชอบความจัดจ้านของรสชาติ ส่วนใครที่ชอบความกลมกล่อม มัน ๆ แบบพรีเมียม “Charlottenbourg” และ “Le Kreuzberg” ก็เป็นตัวเลือกที่ไม่ควรพลาด ทุกชิ้นถูกออกแบบมาให้กินแล้วไม่รู้เลยยยยยยยว่าทำจากโปรตีนที่ผลิตจากจุลินทรีย์ ไม่ใช่นมวัว โดยวางจำหน่ายแล้วในร้านค้ากว่า 2,000 สาขาทั่วเยอรมนีและออสเตรีย ไม่ว่าจะเป็น REWE, BILLA หรือ METRO แปลว่าตลาดเริ่มยอมรับชีสไร้สัตว์ในระดับที่จับต้องได้จริง ไม่ใช่แค่ของเล่นในห้องแล็บอีกต่อไปแล้วครับ มันเกิดขึ้นแล้วในระดับสินค้าบริโภคทั่วไป
ความสำเร็จของ Formo ไม่ได้มาจากเทคโนโลยีอย่างเดียว แต่ยังเกิดจากการสร้างเครือข่ายพันธมิตรและการระดมทุนอย่างชาญฉลาด บริษัทระดมทุนไปแล้วกว่า 135 ล้านยูโรจากนักลงทุนทั่วโลก และได้รับเงินกู้จาก European Investment Bank อีก 35 ล้านยูโร เพื่อนำไปขยายโรงงานผลิตโปรตีนและพัฒนาผลิตภัณฑ์ให้หลากหลายขึ้น รวมถึงลดต้นทุนให้ถูกลง จนสามารถแข่งขันกับชีสจากนมวัวได้ในอนาคต อีกทั้งยังร่วมมือกับบริษัทเบลเยียมอย่าง Those Vegan Cowboys และกลุ่ม Food Fermentation Europe ในการเร่งวิจัยและผลักดันนโยบายให้เทคโนโลยีนี้ได้รับการรับรองในสหภาพยุโรปเร็วขึ้น ซึ่งหากสำเร็จ ก็อาจเป็นจุดเปลี่ยนที่ทำให้ชีสแบบดั้งเดิมต้องยอมหลีกทางให้ชีสจากการหมักอย่างเป็นทางการ
ทั้งหมดนี้ชวนให้เราตั้งคำถามว่า อะไรคือ “ชีสจริง” กันแน่? ถ้าโปรตีนโครงสร้างเหมือนกัน รสชาติเหมือนกัน แต่ผลิตได้อย่างยั่งยืนกว่า สุขภาพดีกว่า และไม่ต้องเบียดเบียนสัตว์ แล้วเรายังจะยึดติดกับภาพวัวนมในทุ่งหญ้าสีเขียวอยู่ไหม? หรือถึงเวลาที่เราจะเปิดใจให้กับชีสแบบใหม่ ที่ไม่ได้มาจากธรรมชาติแบบเดิม ๆ แต่เป็นผลลัพธ์ของความรู้ วิทยาศาสตร์ และความตั้งใจเปลี่ยนแปลงโลกให้การกำหนดอาหารว่า มนุษย์ควรกินอะไร อยู่ภายใต้การผลิตของโรงงาน มากกว่าธรรมชาติ
พรุ่งนี้เราจะมาดูกันครับ ว่าทาสการตลาดจะมองออกไหมว่า สิ่งที่องค์กรเหล่านี้โฆษณาไว้ มีจุดหลบเลี่ยงบาลีอย่างไร ให้แนวทางของเขาดูสวยหรู รักโลก #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 0fa80bd3:ea7325de
2025-01-29 15:43:42
@ 0fa80bd3:ea7325de
2025-01-29 15:43:42Lyn Alden - биткойн евангелист или евангелистка, я пока не понял
npub1a2cww4kn9wqte4ry70vyfwqyqvpswksna27rtxd8vty6c74era8sdcw83aThomas Pacchia - PubKey owner - X - @tpacchia
npub1xy6exlg37pw84cpyj05c2pdgv86hr25cxn0g7aa8g8a6v97mhduqeuhgplcalvadev - Shopstr
npub16dhgpql60vmd4mnydjut87vla23a38j689jssaqlqqlzrtqtd0kqex0nkqCalle - Cashu founder
npub12rv5lskctqxxs2c8rf2zlzc7xx3qpvzs3w4etgemauy9thegr43sf485vgДжек Дорси
npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m21 ideas
npub1lm3f47nzyf0rjp6fsl4qlnkmzed4uj4h2gnf2vhe3l3mrj85vqks6z3c7lМного адресов. Хз кто надо сортировать
https://github.com/aitechguy/nostr-address-bookФиатДжеф - создатель Ностр - https://github.com/fiatjaf
npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6EVAN KALOUDIS Zues wallet
npub19kv88vjm7tw6v9qksn2y6h4hdt6e79nh3zjcud36k9n3lmlwsleqwte2qdПрограммер Коди https://github.com/CodyTseng/nostr-relay
npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wlAnna Chekhovich - Managing Bitcoin at The Anti-Corruption Foundation https://x.com/AnyaChekhovich
npub1y2st7rp54277hyd2usw6shy3kxprnmpvhkezmldp7vhl7hp920aq9cfyr7 -
 @ 378562cd:a6fc6773
2025-05-14 00:10:58
@ 378562cd:a6fc6773
2025-05-14 00:10:58There’s something timeless about the question:
What does it mean to become a man?
It’s been asked around campfires, whispered in barns, shouted across football fields, and wrestled with in the quiet corners of growing hearts.
But the world today is noisy, fast, and confused. We’ve traded compass points for trending hashtags. And yet, the answer hasn’t changed. It’s not in a six-pack, a bank account, or a thousand followers. Manhood isn’t something you perform. It’s something you become. Slowly. Like iron in the fire.
So let’s bring it back. Dust off the old truths. Stir the ashes and tell the tales that forged generations before us.
-
Stand Before the Mirror Without Excuses The first lesson every boy must face is the hardest: You are responsible for yourself. No one else is going to do your pushups. No one else is going to fight your battles. Own your decisions. Own your failures. Own your growth. This isn’t toxic masculinity. It’s accountability. And it’s the foundation for everything else.
-
Work with Your Hands. Sweat with Purpose. You don’t need to be a mechanic or a farmer, but you do need to understand the dignity of labor. Build something. Fix something. Burn blisters into your palms and then look at them with pride. The boy complains about the work. The man shows up anyway, whether raining or shining, and gets it done.
“In the sweat of thy face shalt thou eat bread.” That wasn’t just instruction, it was initiation. A man earns not just his meal, but his manhood, in the honest work of his hands.
-
Learn to Say ‘No’ and Mean It A man who can’t say no will be dragged in every direction but his own. No to cowardice. No to laziness. No to temptation. No to treating people like tools. No to selling your soul for cheap applause. A real man draws lines. And he holds them even if he stands alone.
-
Protect the Vulnerable Your strength isn’t for domination. It’s for protection. The man shields his wife from the chaos, comforts his kids in the dark, and stands before evil, not behind someone else. The strong man doesn’t puff up his chest to impress. He lowers his voice and steadies the room.
And he never lets fear bully the innocent.
-
Speak Less. Do More. The best men I’ve ever met weren’t loud. They were present. They didn’t announce themselves. They didn’t boast. But you felt them in the room. They made eye contact. They kept their word. They listened before speaking. Being a man isn’t about barking orders, and it’s about earning respect quietly and carrying the weight without making others feel it.
-
Know When to Fight and When to Forgive Every young man dreams of being a warrior. But the real test? Knowing which battles matter. A fool fights everything. A coward fights nothing. A man chooses his ground and stands with conviction. But he also knows when to lay it down. To forgive. To rebuild. To let grace triumph over ego.
That’s not weakness. That’s legacy.
-
Seek Wisdom, Not Just Knowledge Read old books. Listen to old men. Ask questions that don’t fit into a TikTok clip. Ask God for wisdom. Wisdom isn’t information, it’s orientation. It’s the difference between knowing how to swing a sword and knowing when to sheath it. A man of wisdom becomes a man of peace. But that peace was earned, not inherited.
-
Be the Man You Needed When You Were a Boy One day, your own shadow will fall across someone smaller than you. A nephew. A son. A kid on the team. Be the man who shows up. The man who teaches gently. The man who isn’t afraid to apologize. You might be the only example they ever see. And you know how that story goes: The boy becomes the man. The man becomes the guide.
-
Walk with God The old path isn’t just about grit. It’s about grace. You were made by design. You were created with purpose. True manhood comes alive when you stop trying to build yourself into a god and instead walk humbly with the One who made you. A man fully submitted to God is a man fully alive. Not perfect. Not polished. But anchored.
Final Thought: The world doesn’t need more influencers. It needs more men. Men of courage. Men of character. Men of consistency. So if you’re reading this and wondering if you’re doing it right, start here:
Take responsibility, love deeply, protect fiercely, walk humbly, work hard, forgive quickly, speak truth, stand firm, and pass it on.
The fire’s still burning, my friend.
Grab an axe.
Become the man.
-
-
 @ 0fa80bd3:ea7325de
2025-01-29 14:44:48
@ 0fa80bd3:ea7325de
2025-01-29 14:44:48![[yedinaya-rossiya-bear.png]]
1️⃣ Be where the bear roams. Stay in its territory, where it hunts for food. No point setting a trap in your backyard if the bear’s chilling in the forest.
2️⃣ Set a well-hidden trap. Bury it, disguise it, and place the bait right in the center. Bears are omnivores—just like secret police KGB agents. And what’s the tastiest bait for them? Money.
3️⃣ Wait for the bear to take the bait. When it reaches in, the trap will snap shut around its paw. It’ll be alive, but stuck. No escape.
Now, what you do with a trapped bear is another question... 😏
-
 @ 0fa80bd3:ea7325de
2025-01-29 05:55:02
@ 0fa80bd3:ea7325de
2025-01-29 05:55:02The land that belongs to the indigenous peoples of Russia has been seized by a gang of killers who have unleashed a war of extermination. They wipe out anyone who refuses to conform to their rules. Those who disagree and stay behind are tortured and killed in prisons and labor camps. Those who flee lose their homeland, dissolve into foreign cultures, and fade away. And those who stand up to protect their people are attacked by the misled and deceived. The deceived die for the unchecked greed of a single dictator—thousands from both sides, people who just wanted to live, raise their kids, and build a future.
Now, they are forced to make an impossible choice: abandon their homeland or die. Some perish on the battlefield, others lose themselves in exile, stripped of their identity, scattered in a world that isn’t theirs.
There’s been endless debate about how to fix this, how to clear the field of the weeds that choke out every new sprout, every attempt at change. But the real problem? We can’t play by their rules. We can’t speak their language or use their weapons. We stand for humanity, and no matter how righteous our cause, we will not multiply suffering. Victory doesn’t come from matching the enemy—it comes from staying ahead, from using tools they haven’t mastered yet. That’s how wars are won.
Our only resource is the will of the people to rewrite the order of things. Historian Timothy Snyder once said that a nation cannot exist without a city. A city is where the most active part of a nation thrives. But the cities are occupied. The streets are watched. Gatherings are impossible. They control the money. They control the mail. They control the media. And any dissent is crushed before it can take root.
So I started asking myself: How do we stop this fragmentation? How do we create a space where people can rebuild their connections when they’re ready? How do we build a self-sustaining network, where everyone contributes and benefits proportionally, while keeping their freedom to leave intact? And more importantly—how do we make it spread, even in occupied territory?
In 2009, something historic happened: the internet got its own money. Thanks to Satoshi Nakamoto, the world took a massive leap forward. Bitcoin and decentralized ledgers shattered the idea that money must be controlled by the state. Now, to move or store value, all you need is an address and a key. A tiny string of text, easy to carry, impossible to seize.
That was the year money broke free. The state lost its grip. Its biggest weapon—physical currency—became irrelevant. Money became purely digital.
The internet was already a sanctuary for information, a place where people could connect and organize. But with Bitcoin, it evolved. Now, value itself could flow freely, beyond the reach of authorities.
Think about it: when seedlings are grown in controlled environments before being planted outside, they get stronger, survive longer, and bear fruit faster. That’s how we handle crops in harsh climates—nurture them until they’re ready for the wild.
Now, picture the internet as that controlled environment for ideas. Bitcoin? It’s the fertile soil that lets them grow. A testing ground for new models of interaction, where concepts can take root before they move into the real world. If nation-states are a battlefield, locked in a brutal war for territory, the internet is boundless. It can absorb any number of ideas, any number of people, and it doesn’t run out of space.
But for this ecosystem to thrive, people need safe ways to communicate, to share ideas, to build something real—without surveillance, without censorship, without the constant fear of being erased.
This is where Nostr comes in.
Nostr—"Notes and Other Stuff Transmitted by Relays"—is more than just a messaging protocol. It’s a new kind of city. One that no dictator can seize, no corporation can own, no government can shut down.
It’s built on decentralization, encryption, and individual control. Messages don’t pass through central servers—they are relayed through independent nodes, and users choose which ones to trust. There’s no master switch to shut it all down. Every person owns their identity, their data, their connections. And no one—no state, no tech giant, no algorithm—can silence them.
In a world where cities fall and governments fail, Nostr is a city that cannot be occupied. A place for ideas, for networks, for freedom. A city that grows stronger the more people build within it.
-
 @ 9e69e420:d12360c2
2025-01-25 22:16:54
@ 9e69e420:d12360c2
2025-01-25 22:16:54President Trump plans to withdraw 20,000 U.S. troops from Europe and expects European allies to contribute financially to the remaining military presence. Reported by ANSA, Trump aims to deliver this message to European leaders since taking office. A European diplomat noted, “the costs cannot be borne solely by American taxpayers.”
The Pentagon hasn't commented yet. Trump has previously sought lower troop levels in Europe and had ordered cuts during his first term. The U.S. currently maintains around 65,000 troops in Europe, with total forces reaching 100,000 since the Ukraine invasion. Trump's new approach may shift military focus to the Pacific amid growing concerns about China.
-
 @ 31a4605e:cf043959
2025-05-13 22:25:08
@ 31a4605e:cf043959
2025-05-13 22:25:08O Bitcoin foi criado como algo muito além de uma moeda digital; ele é uma ideia inovadora que questiona os fundamentos do sistema financeiro convencional. A ideia por trás de sua criação, apresentada pelo enigmático Satoshi Nakamoto, se concentra em dois princípios principais: descentralização e liberdade financeira. Essas noções refletem um esforço para devolver o controle do dinheiro às pessoas, eliminando intermediários e diminuindo a influência de governos e grandes instituições financeiras.
A descentralização é a base do Bitcoin. Diferente das moedas comuns, que são emitidas e geridas por bancos centrais e governos, o Bitcoin funciona em uma rede peer-to-peer. Isso quer dizer que não existe uma autoridade central ou entidade única que controla a moeda. Ao invés disso, todas as transações são validadas e registradas em um livro-razão público chamado blockchain ou timechain, mantido por milhares de computadores em várias partes do mundo.
Essa estrutura descentralizada garante que o Bitcoin seja resistente à censura e imune a manipulações de políticas monetárias, como a impressão excessiva de dinheiro, que pode causar inflação. Além disso, ela elimina a necessidade de intermediários, como bancos, permitindo transações diretas entre usuários. Isso é especialmente valioso em cenários onde o sistema bancário tradicional é inacessível ou composto, como em áreas remotas ou países em crise econômica.
A liberdade financeira promovida pelo Bitcoin é outro elemento transformador. Em sistemas tradicionais, os indivíduos dependem de terceiros, como bancos ou instituições financeiras, para acessar, guardar e transferir dinheiro. Essas entidades podem impor restrições, como limites de saque, altas taxas de transferência ou até mesmo bloquear contas. Com o Bitcoin, o usuário possui controle total sobre seus fundos através de chaves privadas (uma espécie de senha que possibilita o acesso à sua carteira digital).
Além disso, o Bitcoin oferece uma solução acessível para bilhões de pessoas no mundo que estão fora do sistema bancário. Segundo dados do Banco Mundial, cerca de 1,4 bilhão de adultos não têm acesso a contas bancárias, mas muitos têm acesso à internet ou a smartphones. O Bitcoin permite que essas pessoas participem da economia global sem a necessidade de instituições intermediárias.
Outro ponto importante é a resistência à censura. Em regimes autoritários ou situações de instabilidade política, governos podem confiscar ou bloquear os bens dos cidadãos. O Bitcoin, por ser descentralizado e operar em uma rede global, não pode ser controlado ou confiscado de maneira arbitrária, oferecendo uma camada extra de proteção financeira para indivíduos em situações de risco.
A visão do Bitcoin também abrange a formação de um sistema financeiro mais justo e transparente. O blockchain ou timechain, ao registrar todas as transações de modo público e imutável, diminui a chance de fraudes e corrupção. Além disso, a quantidade limitada de 21 milhões de bitcoins, programada no código da moeda, favorece um modelo deflacionário que contrasta com a expansão ilimitada de moedas fiduciárias. Isso confere ao Bitcoin a capacidade de ser uma reserva de valor estável no longo prazo.
Apesar de sua visão promissora, o caminho para alcançar completamente essa liberdade financeira não é livre de desafios. A volatilidade do preço do Bitcoin, preocupações regulatórias e barreiras tecnológicas ainda são obstáculos a serem superados. No entanto, essas dificuldades também criam oportunidades para inovação e para o fortalecimento do ecossistema ao longo do tempo.
Resumindo, a visão por trás do Bitcoin representa uma interrupção do sistema financeiro centralizado, oferecendo às pessoas mais autonomia, transparência e segurança sobre seus recursos financeiros. Ele não é apenas uma tecnologia, mas um movimento que busca empoderar os indivíduos, especialmente aqueles excluídos ou prejudicados pelos modelos econômicos tradicionais. Ao promover descentralização e liberdade financeira, o Bitcoin abre caminho para um futuro onde o dinheiro realmente pertence às pessoas, e não às instituições.
Muito obrigado por teres lido o texto até aqui, espero que esteja tudo bem contigo e um abraço enorme do teu madeirense bitcoiner maximalista favorito. Viva a liberdade!
-
 @ 31a4605e:cf043959
2025-05-13 22:22:20
@ 31a4605e:cf043959
2025-05-13 22:22:20Bitcoin é a primeira moeda digital descentralizada do mundo, criada em 2009 por um indivíduo ou grupo sob o pseudônimo de Satoshi Nakamoto. O seu nascimento marcou o início de uma revolução no sistema financeiro global, introduzindo um novo tipo de moeda que não é controlada pelos governos ou instituições financeiras tradicionais. A história do Bitcoin está profundamente enraizada nos ideais de liberdade económica, transparência e resistência à censura.
A jornada começou em outubro de 2008, quando Satoshi Nakamoto publicou um artigo intitulado “Bitcoin: A Peer-to-Peer Electronic Cash System”. O white paper, publicado na mailing list Cryptozoology, descreve a ideia de um sistema de pagamento digital baseado em uma rede peer-to-peer. Esse conceito elimina a necessidade de intermediários como bancos e resolve um problema conhecido como “gasto duplo” – possibilidade de replicação de moedas digitais – por meio de uma tecnologia chamada blockchain ou aquilo que o próprio Satoshi Nakamoto chamava de timechain.
O blockchain ou timechain é basicamente um livro-razão público e imutável que registra todas as transações do Bitcoin. Opera através de um sistema descentralizado, onde os participantes da rede (os chamados nós ou famosos nodes) verificam as transações e as organizam em blocos. Esses blocos são conectados por sua vez em uma cadeia contínua, formando a base para a segurança e transparência do sistema.
No dia 3 de janeiro de 2009, Satoshi Nakamoto extraiu o primeiro bloco do Bitcoin, conhecido como bloco gênese. O bloco continha uma mensagem codificada referenciando a crise financeira global de 2008: "The Times, 3 de janeiro de 2009, Chanceler à beira do segundo resgate bancário". Esta mensagem é emblemática da motivação por trás do Bitcoin: fornecer uma alternativa ao sistema financeiro centralizado que não conseguiu proteger a economia global.
Ao longo de 2009 e 2010, o Bitcoin permaneceu como um experimento entre os entusiastas da tecnologia e das criptomoedas. As primeiras transações de Bitcoin ocorreram entre participantes da rede, e o primeiro uso comercial da moeda ocorreu em 22 de maio de 2010, quando um programador chamado Laszlo Hanyecz comprou duas pizzas por 10 mil Bitcoins. Esta transação histórica foi apelidada de “Bitcoin Pizza Day”.
Satoshi Nakamoto continuou a contribuir para o desenvolvimento do Bitcoin até o final de 2010, quando desapareceu gradualmente da comunidade. Até hoje, sua identidade permanece um mistério e não há evidências concretas de quem ou quantas pessoas estavam por trás do pseudônimo. Antes de sair, Satoshi Nakamoto entregou o controle do projeto a outros desenvolvedores e deixou claro que o Bitcoin deveria ser uma tecnologia descentralizada, de propriedade de todos e controlada por ninguém.
Desde então, o Bitcoin cresceu exponencialmente. Cresceu de um experimento tecnológico para um ativo multibilionário e é amplamente considerada a forma legítima de moeda digital e reserva de valor. Governos, empresas e indivíduos em todo o mundo adotaram o Bitcoin como alternativa às moedas fiat tradicionais.
Resumindo, a criação do Bitcoin por Satoshi Nakamoto foi mais do que apenas o nascimento de uma moeda digital; Este foi o início de um movimento global para repensar a forma como o dinheiro é controlado e distribuído. Embora a identidade de Satoshi Nakamoto permaneça desconhecida, o seu legado continuará a moldar o futuro do sistema financeiro e a desafiar as estruturas económicas tradicionais.
Muito obrigado por teres lido o texto até aqui, espero que esteja tudo bem contigo e um abraço enorme do teu madeirense bitcoiner maximalista favorito. Viva a liberdade!
-
 @ 6be5cc06:5259daf0
2025-01-21 20:58:37
@ 6be5cc06:5259daf0
2025-01-21 20:58:37A seguir, veja como instalar e configurar o Privoxy no Pop!_OS.
1. Instalar o Tor e o Privoxy
Abra o terminal e execute:
bash sudo apt update sudo apt install tor privoxyExplicação:
- Tor: Roteia o tráfego pela rede Tor.
- Privoxy: Proxy avançado que intermedia a conexão entre aplicativos e o Tor.
2. Configurar o Privoxy
Abra o arquivo de configuração do Privoxy:
bash sudo nano /etc/privoxy/configNavegue até a última linha (atalho:
Ctrl+/depoisCtrl+Vpara navegar diretamente até a última linha) e insira:bash forward-socks5 / 127.0.0.1:9050 .Isso faz com que o Privoxy envie todo o tráfego para o Tor através da porta 9050.
Salve (
CTRL+OeEnter) e feche (CTRL+X) o arquivo.
3. Iniciar o Tor e o Privoxy
Agora, inicie e habilite os serviços:
bash sudo systemctl start tor sudo systemctl start privoxy sudo systemctl enable tor sudo systemctl enable privoxyExplicação:
- start: Inicia os serviços.
- enable: Faz com que iniciem automaticamente ao ligar o PC.
4. Configurar o Navegador Firefox
Para usar a rede Tor com o Firefox:
- Abra o Firefox.
- Acesse Configurações → Configurar conexão.
- Selecione Configuração manual de proxy.
- Configure assim:
- Proxy HTTP:
127.0.0.1 - Porta:
8118(porta padrão do Privoxy) - Domínio SOCKS (v5):
127.0.0.1 - Porta:
9050
- Proxy HTTP:
- Marque a opção "Usar este proxy também em HTTPS".
- Clique em OK.
5. Verificar a Conexão com o Tor
Abra o navegador e acesse:
text https://check.torproject.org/Se aparecer a mensagem "Congratulations. This browser is configured to use Tor.", a configuração está correta.
Dicas Extras
- Privoxy pode ser ajustado para bloquear anúncios e rastreadores.
- Outros aplicativos também podem ser configurados para usar o Privoxy.
