-
 @ df67f9a7:2d4fc200
2025-06-05 19:52:32
@ df67f9a7:2d4fc200
2025-06-05 19:52:32Nostr is NOT a social network. Nostr is a network of interconnected social apps. And, since any app is a social app, Nostr is for every app.
ONLY Nostr incentivizes inter-connectivity between independent apps, simply by respecting sovereignty at the protocol layer. For end users, sovereignty means that the content they post “to Nostr” will never be owned by the apps that they use. For businesses building apps on Nostr, sovereignty means that every app actually benefits by other apps being on the network. Because sovereignty is respected, users are retained for longer and independent apps thrive far longer on Nostr than on the legacy “black box” social networks.
Social apps thrive on Nostr
Nostr integration provides these benefits for every app :
- Unrestrained access for any app, to all public and private data “on Nostr”. No fees or licenses for harvesting user data from the network.
- Unburdened from liability, when collecting user data with any app. When sending “to Nostr”, end users retain custody of user data while apps never loose access.
- Unlimited free market of search engines and feed algos. Users and brands can create, use, and share any algos or custom feeds. Grow your audience on your own terms.
- Universal open network for all apps. Build any kind of app for any audience, on the same network as other apps for other audiences. Discover new trends from user data.
- Unregulated tech platform. Build your own app and use it as you wish. No gate keepers. No code review.
Sovereignty is good for business.
Regardless of the network size, a Nostr integrated app can grow its user base MUCH faster and with greater independence BECAUSE of the sovereignty respecting protocol. While end users may retain custody of their identities and data on the network, it’s the apps that determine which data is, or is not, sent to the network. Respect for sovereignty IS the killer feature that ONLY the Nostr protocol provides for apps and for end users.
Because Nostr is permissionless for any app to integrate :
- end users will always have a free market of apps choose from
- apps are free to integrate only as much as benefits their business model.
- apps gain access to more novel data as new apps bring new users to the network.
Because data on Nostr is managed by end users and available to all apps :
- User data looses exclusivity and the demand shifts toward novel insights and information derived from these data.
- Apps are freed from having to be “data pirates”, and can focus on establishing a trusted user base, providing valuable services to satisfied customers, informed by the abundance of user data.
- Apps are incentivized to offload data onto the network, establishing a new paradigm for interconnectivity, where independence is NOT at stake as the network grows.
- New markets spring up to support users with self custody of their data, driven by the reality that apps can have full access without assuming responsibility.
- The market for search and algo tools opens up for independent apps and end users to discover and interact freely with each other.
- The ad based “attention economy” slowly transforms to a value based consumer economy, where the end user is the customer rather than the product being sold.
Even while privacy is respected
Sometimes sovereignty is at odds with privacy, but Nostr allows all parties to win while both are protected.
- For end users sending sensetive data "to Nostr", privacy is assured by encrypting it with their own private keys and/or sending it to private (auth required) relays of their choosing.
- For apps handling private IP or business data, any traditional “black box” infrastructure can be used in the back end to manitain isolation from Nostr.
This means apps and end users remain in control of their own private data, without requiring “big social” as trust provider or data reseller. To access a user's private data, client apps (even search engines, running locally) only need explicit permission from the end user to retrieve or decrypt from Nostr relays. Public data, on the other hand, is freely available for any app or search engine to harvest from any Nostr relay. In either case, user data on the Nostr network is always accessible to client apps, without additional restrictions or fees.
Nostr is for every app.
Adding social to any app makes it a better app. Add reviews for products or services. Add commenting or direct messaging. Share or collaborate on content creation. Nostr integration is straightforward and incremental for any app.
Nostr doesn't define your app's business model ... Nostr 10X's it!
Here's how :
- Start with your own business and app design. Add Nosrr login.
- Discover what "kinds" of user data already exists "on Nostr" that your app can ingest and make use of.
- Decide which "kinds" of data would benefit your business, your users, and the network, if sent "to Nostr".
- Implement Nostr integration for data kinds and add webs of trust tools for recommendation and discovery.
- Verify your app is sovereignty respecting in how it handles private data and implements Nostr NIPs.
- Engage with existing users, and onboard new users from your app, to earn their trust and patronage over Nostr.
For more info and assistance, contact our team of Nostr integration experts.
-
 @ 90c656ff:9383fd4e
2025-06-05 12:27:43
@ 90c656ff:9383fd4e
2025-06-05 12:27:43When people talk about Bitcoin, it’s often described as a digital currency or a “speculative investment.” However, one of Bitcoin’s most fundamental and least understood roles is its function as a settlement network. To understand this, it’s worth comparing it with traditional settlement systems like SWIFT and exploring how Bitcoin offers a foundational layer for global value transfer decentralized and censorship-resistant.
First, let’s explain the difference between liquidity and settlement:
-
Liquidity refers to the ease with which an asset can be converted into “money” without losing value.
-
Settlement is the process of completing a transaction (actual transfer of value between parties).
SWIFT: The communication layer of the traditional financial system
The SWIFT system (Society for Worldwide Interbank Financial Telecommunication) is a network for communication between banks. It doesn’t move money directly but sends standardized messages that instruct financial institutions to perform transfers. The process involves multiple intermediaries, is costly, slow (can take days), and depends on trust between parties and local regulations.
Unlike SWIFT, Bitcoin is a self-sufficient network that enables the direct settlement of value between two parties, without the need for intermediaries. With each block mined, transactions are validated and recorded immutably in a global, transparent, and secure database: the timechain or "blockchain".
01 - Final settlement: Once a transaction is confirmed by a sufficient number of blocks, it is considered final and irreversible.
02 - Censorship resistance: There is no central entity that can block or reverse a valid transaction.
03 - Global availability: The network is accessible 24/7 anywhere in the world with internet access.
Just as gold once served as the foundation of monetary systems, Bitcoin is establishing itself as a base layer of digital value. This layer can support others, such as:
01 - The Lightning Network, which enables near-instant transactions with extremely low fees;
02 - Tokenized financial services, which can use Bitcoin as collateral or for inter-institutional settlement.
By functioning as a public and neutral settlement network, Bitcoin offers an alternative to the traditional system, which is fragmented, closed, and reliant on trust between institutions.
In summary, more than just a speculative asset, Bitcoin is emerging as a global financial infrastructure. As a settlement network, it removes intermediaries, reduces costs, increases security, and democratizes access to value transfer. In an increasingly interconnected and digital world, understanding Bitcoin’s role as a base layer may be key to understanding the future of money.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
-
 @ b1ddb4d7:471244e7
2025-06-05 10:00:43
@ b1ddb4d7:471244e7
2025-06-05 10:00:43Starting January 1, 2026, the United Kingdom will impose some of the world’s most stringent reporting requirements on cryptocurrency firms.
All platforms operating in or serving UK customers-domestic and foreign alike-must collect and disclose extensive personal and transactional data for every user, including individuals, companies, trusts, and charities.
This regulatory drive marks the UK’s formal adoption of the OECD’s Crypto-Asset Reporting Framework (CARF), a global initiative designed to bring crypto oversight in line with traditional banking and to curb tax evasion in the rapidly expanding digital asset sector.
What Will Be Reported?
Crypto firms must gather and submit the following for each transaction:
- User’s full legal name, home address, and taxpayer identification number
- Detailed data on every trade or transfer: type of cryptocurrency, amount, and nature of the transaction
- Identifying information for corporate, trust, and charitable clients
The obligation extends to all digital asset activities, including crypto-to-crypto and crypto-to-fiat trades, and applies to both UK residents and non-residents using UK-based platforms. The first annual reports covering 2026 activity are due by May 31, 2027.
Enforcement and Penalties
Non-compliance will carry stiff financial penalties, with fines of up to £300 per user account for inaccurate or missing data-a potentially enormous liability for large exchanges. The UK government has urged crypto firms to begin collecting this information immediately to ensure operational readiness.
Regulatory Context and Market Impact
This move is part of a broader UK strategy to position itself as a global fintech hub while clamping down on fraud and illicit finance. UK Chancellor Rachel Reeves has championed these measures, stating, “Britain is open for business – but closed to fraud, abuse, and instability”. The regulatory expansion comes amid a surge in crypto adoption: the UK’s Financial Conduct Authority reported that 12% of UK adults owned crypto in 2024, up from just 4% in 2021.
Enormous Risks for Consumers: Lessons from the Coinbase Data Breach
While the new framework aims to enhance transparency and protect consumers, it also dramatically increases the volume of sensitive personal data held by crypto firms-raising the stakes for cybersecurity.
The risks are underscored by the recent high-profile breach at Coinbase, one of the world’s largest exchanges.
In May 2025, Coinbase disclosed that cybercriminals, aided by bribed offshore contractors, accessed and exfiltrated customer data including names, addresses, government IDs, and partial bank details.
The attackers then used this information for sophisticated phishing campaigns, successfully deceiving some customers into surrendering account credentials and funds.
“While private encryption keys remained secure, sufficient customer information was exposed to enable sophisticated phishing attacks by criminals posing as Coinbase personnel.”
Coinbase now faces up to $400 million in compensation costs and has pledged to reimburse affected users, but the incident highlights the systemic vulnerability created when large troves of personal data are centralized-even if passwords and private keys are not directly compromised. The breach also triggered a notable drop in Coinbase’s share price and prompted a $20 million bounty for information leading to the attackers’ capture.
The Bottom Line
The UK’s forthcoming crypto reporting regime represents a landmark in financial regulation, promising greater transparency and tax compliance. However, as the Coinbase episode demonstrates, the aggregation of sensitive user data at scale poses a significant cybersecurity risk.
As regulators push for more oversight, the challenge will be ensuring that consumer protection does not become a double-edged sword-exposing users to new threats even as it seeks to shield them from old ones.
-
 @ 3eab247c:1d80aeed
2025-06-05 08:51:39
@ 3eab247c:1d80aeed
2025-06-05 08:51:39Global Metrics
Here are the top stats from the last period:
- Total Bitcoin-accepting merchants: 15,306 → 16,284
- Recently verified (1y): 7,540 → 7,803 (the rest of our dataset is slowly rotting; help us before it's too late!)
- Avg. days since last verification: 398 → 405 (more mappers, please)
- Merchants boosted: 22 (for a total of 4,325 days, someone is feeling generous)
- Comments posted: 34
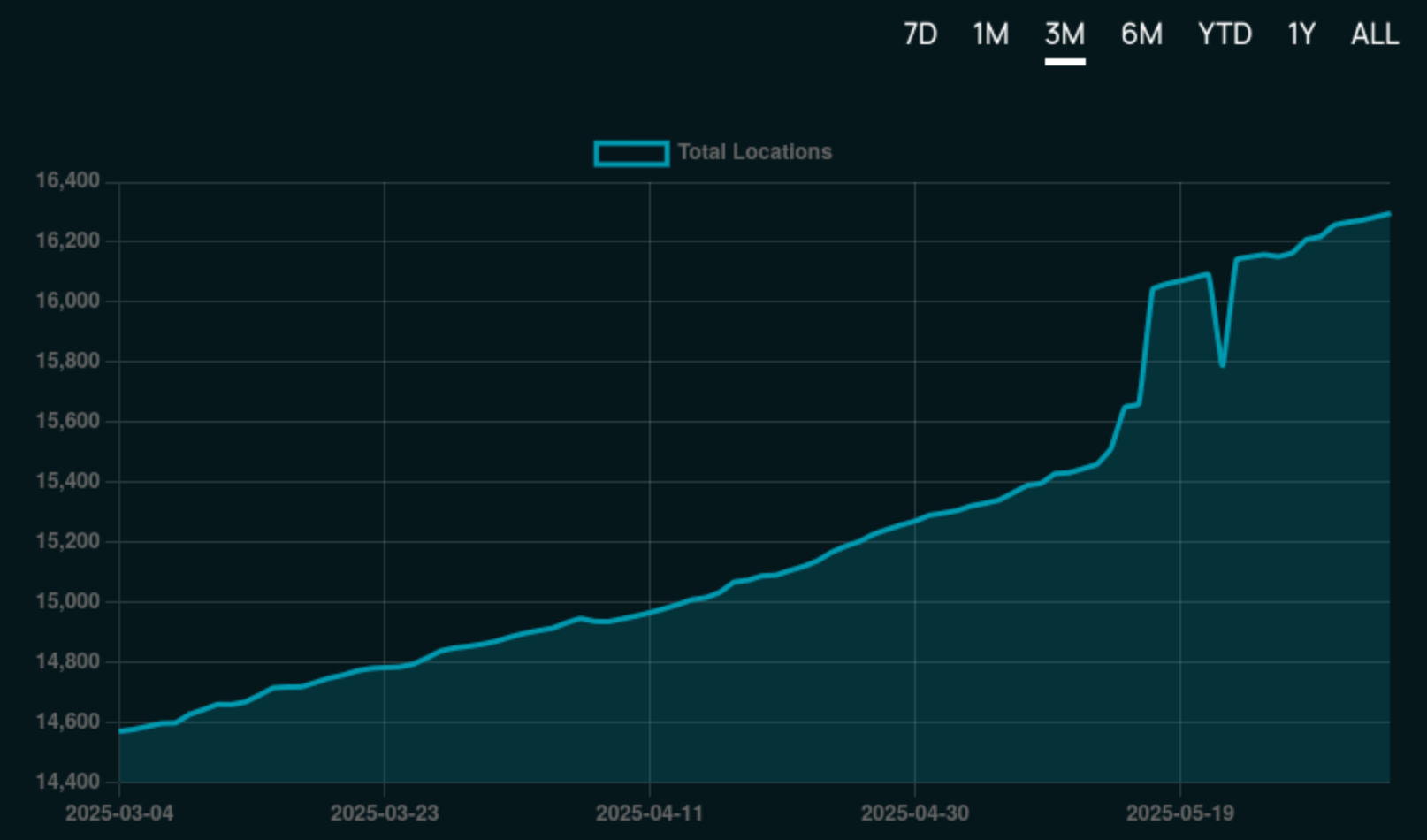
Find current stats over at the 👉 BTC Map Dashboard.
Merchant Adoption
Steak n’ Shake
The US 🇺🇸 is a massive country, yet its BTC Map footprint has been lagging relative to other countries ... that is until now!

In what came as a nice surprise to our Shadowy Supertaggers 🫠, the Steak ’n Shake chain began accepting Bitcoin payments across hundreds of its locations nationwide (with some international locations too).
According to CoinDesk, the rollout has been smooth, with users reporting seamless transactions powered by Speed.
This marks a significant step towards broader Bitcoin adoption in the US. Now to drop the capital gains tax on cheesburgers!
SPAR Switzerland
In other chain/franchise adoption news, the first SPAR supermarket in Switzerland 🇨🇭 to begin accepting Bitcoin was this one in Zug. It was quickly followed by this one in Rossrüti and this one in Kreuzlingen, in what is believed to be part of a wider roll-out plan within the country powered by DFX's Open CryptoPay.
That said, we believe the OG SPAR crown goes to SPAR City in Arnhem Bitcoin City!
New Features
Merchant Comments in the Web App
Web App users are now on par with Android users in that they can both see and make comments on merchants.
This is powered by our tweaked API that enables anyone to make a comment as long as they pass the satswall fee of 500 sats. This helps keep spam manageable and ensure quality comments.
And just in case you were wondering what the number count was on the merchant pins - yep, they're comments!
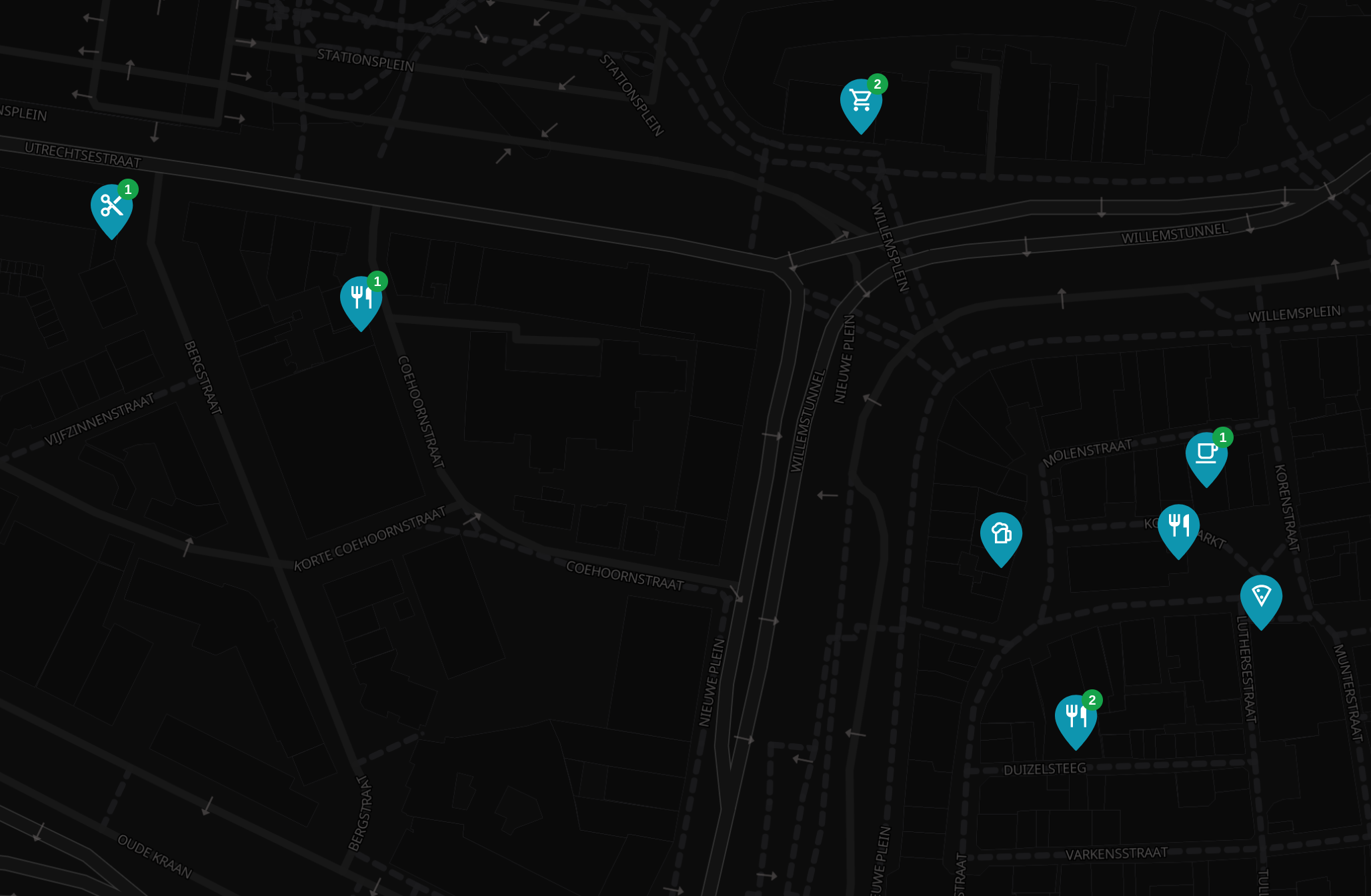
Here is an 👉 Example merchant page with comments.
Merchant Page Design Tweaks
To support the now trio of actions (Verify, Boost & Comment) on the merchant page, we've re-jigged the design a little to make things a little clearer.
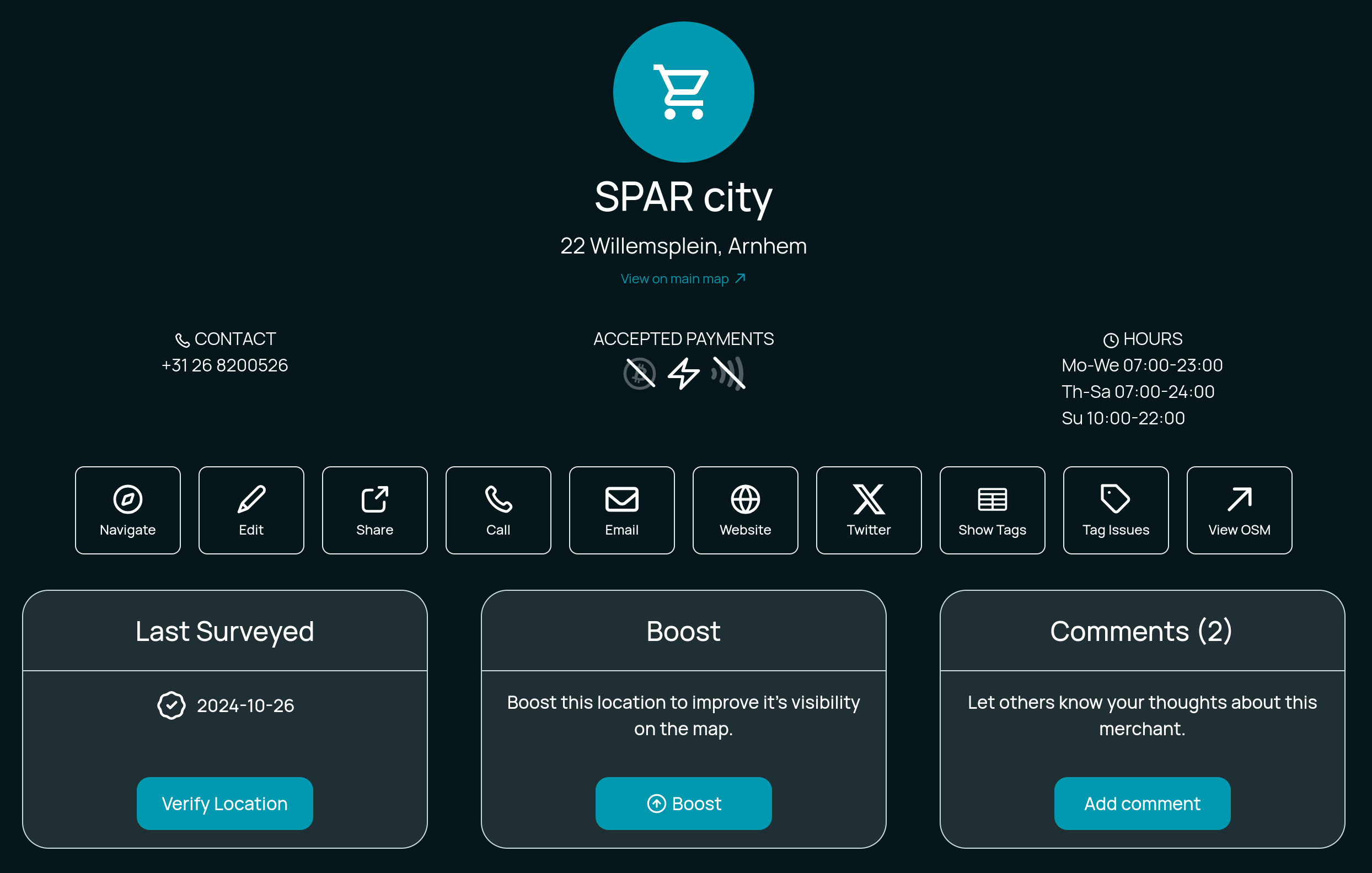
What do you think?
Technical
Codebase Refactoring
Thanks to Hannes’s contributions, we’ve made progress in cleaning-up the Web App's codebase and completing long overdue maintenance. Whilst often thankless tasks, these caretaking activities help immensely with long-term maintainability enabling us to confidently build new features.
Auth System Upgrades
The old auth system was held together with duct tape and prayers, and we’re working on a more robust authentication system to support future public API access. Updates include:
- Password hashing
- Bearer token support
- Improved security practices
More enhancements are in progress and we'll update you in the next blog post.
Better API Documentation
Instead of relying on tribal knowledge, we're finally getting around to writing actual docs (with the help/hindrance of LLMs). The "move fast, break everything" era is over; now we move slightly slower and break slightly less. Progress!
Database Improvements
We use SQLite, which works well but it requires careful handling in async Rust environments. So now we're untangling this mess to avoid accidental blocking queries (and the ensuing dumpster fires).
Backup System Enhancements
BTC Map data comes in three layers of fragility:
- Merchants (backed up by OS - the big boys handle this)
- Non-OSM stuff (areas, users, etc. - currently stored on a napkin)
- External systems (Lightning node, submission tickets - pray to Satoshi)
We're now forcing two core members to backup everything, because redundancy is good.
Credits
Thanks to everyone who directly contributed to the project this period:
- Comino
- descubrebitcoin
- Hannes
- Igor Bubelov
- Nathan Day
- Rockedf
- Saunter
- SiriusBig
- vv01f
Support Us
There are many ways in which you can support us:
-
Become a Shadowy Supertagger and help maintain your local area or pitch-in with the never-ending global effort.
-
Consider a zapping this note or make a donation to the to the project here.
-
 @ 472f440f:5669301e
2025-06-04 20:58:53
@ 472f440f:5669301e
2025-06-04 20:58:53Marty's Bent
J.P. Morgan CEO Jamie Dimon has long been an outspoken skeptic and critic of bitcoin. He has called Bitcoin a speculative asset, a fraud, a pet rock, and has opined that it will inevitably blow up. A couple of years ago, he was on Capitol Hill saying that if he were the government, he would "close it down". Just within the last month, he was on Fox Business News talking with Maria Bartiromo, proclaiming that the U.S. should be stockpiling bullets and rare earth metals instead of bitcoin. It's pretty clear that Jamie Dimon, who is at the helm of the most powerful and largest bank in the world, does not like bitcoin one bit.
Evidence below:

via Bitcoin Magazine

via me
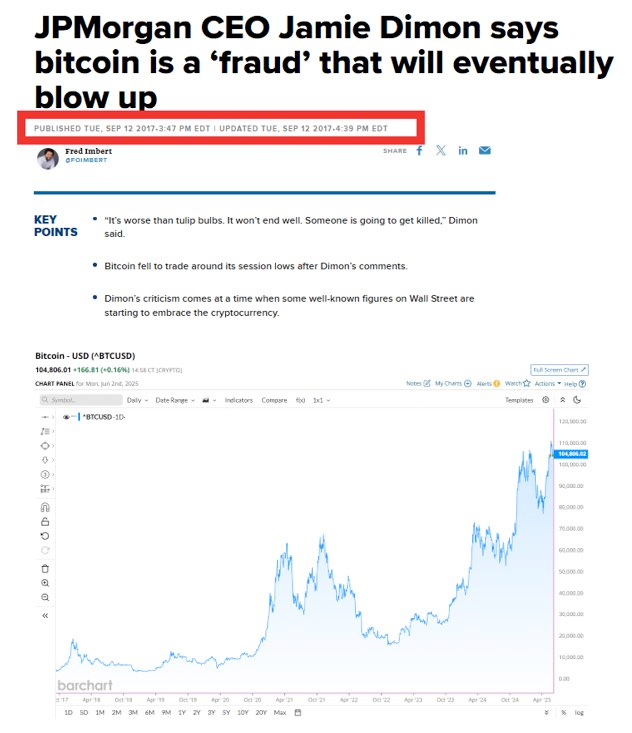
via CNBC

Despite Dimon's distinguished disdain for Bitcoin, J.P. Morgan cannot deny reality. The CEO of the largest bank in the world is certainly a powerful man, but no one individual, even in the position that Jamie Dimon is in, is more powerful than the market. And the market has spoken very clearly, it is demanding bitcoin. The Bitcoin ETFs have been the most successful ETFs in terms of pace of growth since their launch. They've accumulated tens of billions of dollars in AUM in a very short period of time. Outpacing the previous record set by the gold ETF, GLD.
Whether or not Jamie Dimon himself likes Bitcoin doesn't matter. J.P. Morgan, as the largest bank in the world and a publicly traded company, has a duty to shareholders. And that duty is to increase shareholder value by any ethical and legal means necessary. Earlier today, J.P. Morgan announced plans to offer clients financing against their Bitcoin ETFs, as well as some other benefits, including having their bitcoin holdings recognized in their overall net worth and liquid assets, similar to stocks, cars, and art, which will be massive for bitcoiners looking to get mortgages and other types of loans.

via Bloomberg
I've talked about this recently, but trying to buy a house when most of your liquid net worth is held in bitcoin is a massive pain in the ass. Up until this point, if you wanted to have your bitcoin recognized as part of your net worth and count towards your overall credit profile, you would need to sell some bitcoin, move it to a bank account, and have it sit there for a certain period of time before it was recognized toward your net worth. This is not ideal for bitcoiners who have sufficient cash flows and don't want to sell their bitcoin, pay the capital gains tax, and risk not being able to buy back the amount of sats they were forced to sell just to get a mortgage.
It's not yet clear to me whether or not J.P. Morgan will recognize bitcoin in cold storage toward their clients' net worth and credit profile, or if this is simply for bitcoin ETFs only. However, regardless, this is a step in the right direction and a validation of something that many bitcoiners have been saying for years. Inevitably, everyone will have to bend the knee to bitcoin. Today, it just happened to be the largest bank in the world. I expect more of this to come in the coming months, years, and decades.
Lyn Alden likes to say it in the context of the U.S. national debt and the fiscal crisis, but it also applies to bitcoin adoption and the need for incumbents to orient themselves around the demands of individual bitcoiners; nothing stops this train.
Corporate Bitcoin Treasuries are Changing Market Dynamics
Leon Wankum revealed how corporate Bitcoin treasuries are fundamentally reshaping business dynamics. Companies can now issue equity to fund operations while preserving their Bitcoin holdings, creating a revolutionary capital structure. Leon highlighted MicroStrategy's position, noting they hold enough Bitcoin to cover dividend payments for over 200 years. This model enables companies to reduce founder dilution since they don't need repeated funding rounds when their treasury appreciates.
"Some companies' Bitcoin treasuries are now worth more than all money they've ever raised." - Leon Wankum
Leon shared examples from his own portfolio companies where this strategy has proven transformative. Public companies have discovered an entirely new business model through strategic dilution that actually increases BTC per share. As Leon explained, this approach allows firms to leverage equity markets for operational funding while their Bitcoin treasury compounds in value, creating a positive feedback loop that benefits both shareholders and the company's long-term sustainability.
Check out the full podcast here for more on real estate price cycles, Bitcoin lending products, and the transition to a Bitcoin standard.
Headlines of the Day
California May Seize Idle Bitcoin After 3 Years - via X
Semler Scientific Buys $20M More Bitcoin, Holds $467M - via X
US Home Sellers Surge as Buyers Hit 4-Year Low - via X
Get our new STACK SATS hat - via tftcmerch.io
Take the First Step Off the Exchange
Bitkey is an easy, secure way to move your Bitcoin into self-custody. With simple setup and built-in recovery, it’s the perfect starting point for getting your coins off centralized platforms and into cold storage—no complexity, no middlemen.
Take control. Start with Bitkey.
Use the promo code “TFTC20” during checkout for 20% off
Ten31, the largest bitcoin-focused investor, has deployed $150.00M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/invest.
Final thought...
I feel old.
Get this newsletter sent to your inbox daily: https://www.tftc.io/bitcoin-brief/
Subscribe to our YouTube channels and follow us on Nostr and X:
-
 @ e516ecb8:1be0b167
2025-06-04 20:33:38
@ e516ecb8:1be0b167
2025-06-04 20:33:38Imagina un mundo donde cada peso que gastas es vigilado, registrado y cuestionado. Donde el Estado decide si puedes comprar un café, una manzana o una criptomoneda. No es una distopía de ciencia ficción, es el rumbo que están tomando varios países, mientras otros, como Argentina, dan un giro inesperado hacia la libertad. ¿Quién está ganando esta batalla por el control de tu dinero?
Argentina: "Tus dólares son tuyos" En Argentina, Javier Milei, con su bandera libertaria ondeando, ha dado un paso audaz: desmantelar el control policial sobre el dinero de los ciudadanos. Su lema, "Tus dólares son tuyos", es tan obvio como revolucionario. Después de décadas de corralitos, cepos cambiarios y una inflación que en 2023 alcanzó el 211,4% según el INDEC, Milei apuesta por devolverle al ciudadano el poder sobre su propio capital. Con el país logrando superávit fiscal por primera vez en años (0,2% del PBI en el primer trimestre de 2024), el gobierno ya no necesita espiar cada transacción para exprimir impuestos.
Pero aquí viene lo curioso: encuestas recientes, como una de la consultora Poliarquía, muestran que un 35% de los argentinos aún prefiere que el Estado controle sus finanzas. ¿Masoquismo? ¿Miedo a la libertad? Tal vez sea la costumbre de vivir bajo la lupa. Milei, fiel a su convicción, no solo liberaliza por necesidad económica, sino porque cree que el dinero es tuyo, no del burócrata de turno.
España y el Euro Digital: El ojo que todo lo ve Mientras Argentina afloja las riendas, Europa cabalga en dirección opuesta. En España, el gobierno está reduciendo progresivamente los umbrales para controlar transacciones bancarias. A partir de 2026, cada pago por Bizum —el equivalente ibérico al Pix brasileño— estará bajo escrutinio. Según el Banco de España, en 2024 se realizaron más de 1.200 millones de transacciones por Bizum, moviendo unos 60.000 millones de euros. Ahora, cada una de esas operaciones será un dato más para Hacienda.
Pero no es solo España. La Unión Europea avanza con el Euro Digital, un proyecto que promete ser la pesadilla de cualquier amante de la privacidad. Esta moneda digital, según el Banco Central Europeo, permitirá rastrear cada movimiento, limitar ciertos gastos (¿adiós a compras de cripto o donaciones incómodas?), e incluso programar que el dinero "se oxide". Sí, has leído bien: si no gastas tus euros digitales en un tiempo determinado, podrían perder valor o simplemente desaparecer. Un informe del BCE de 2023 estima que el Euro Digital estará operativo en 2027, y ya hay pruebas piloto en países como Alemania y Francia. ¿Libertad financiera? Más bien un Gran Hermano con esteroides.
Chile: El Estado fisgón y los funcionarios de lujo En Chile, el control monetario también aprieta. El gobierno ha propuesto levantar el secreto bancario, permitiendo que cualquier funcionario del SII pueda husmear en tus cuentas. Además, si haces más de 50 transacciones al mes, el Servicio de Impuestos Internos (SII) pondrá la lupa sobre ti. ¿Y las ferias libres? Esas donde compras tus tomates y zapallos sin complicaciones ahora deberán emitir boletas electrónicas, encareciendo los productos para el ciudadano de a pie. Según la CEPAL, los costos administrativos para pequeños comerciantes podrían aumentar hasta un 15% con estas medidas.
Mientras tanto, el sector público chileno vive en otra galaxia. Funcionarios con sueldos que superan los 5 millones de pesos mensuales (unos 5.500 USD) toman licencias médicas para viajar por el mundo, según denuncias de la Contraloría. Algunos incluso cobran por "turnos" de 17 horas extras diarias o marcan asistencia en dos lugares al mismo tiempo. ¿Y quién paga? Tú, con tus impuestos.
La resistencia: Volver al efectivo o abrazar las cripto Si el Estado quiere controlar cada centavo, ¿qué opciones nos quedan? Una es volver al efectivo, pero no nos engañemos: el dinero fiat, controlado por bancos centrales, pierde valor a largo plazo. En Chile, la inflación acumulada entre 2010 y 2024 fue del 62%, según el INE. Tus billetes de hoy valen menos que los de ayer, y mañana valdrán aún menos.
La otra opción es el mundo cripto, pero no cualquier cripto. Bitcoin, la más conocida, es un titán para almacenar valor, pero para transacciones diarias necesita una segunda capa como Lightning Network, que procesa pagos instantáneos con comisiones ínfimas (menos de 0,01 USD por transacción en 2024). Alternativas como Bitcoin Cash (BCH) o Monero (XMR) ofrecen transacciones rápidas y, en el caso de XMR, un enfoque en la privacidad que hace temblar a los burócratas. Sin embargo, ninguna cripto servirá si los comercios y las personas no las adoptan. En Argentina, por ejemplo, solo el 1,5% de las transacciones minoristas en 2024 usaron criptomonedas, según Chainalysis. La libertad financiera no llega sola: hay que construirla.
El futuro es ahora El dinero es poder, y quien controla el dinero controla tu vida. Mientras Milei en Argentina te devuelve las llaves de tus dólares, en Europa y Chile te atan las manos con leyes, regulaciones y monedas digitales. La pregunta no es si quieres libertad, sino si estás dispuesto a pelear por ella. Usa efectivo, explora cripto, pero sobre todo, no dejes que el Gran Hermano decida por ti. Porque una vez que el Estado mete la mano en tu bolsillo, no la saca nunca.
-
 @ ca76c778:e784c54b
2025-06-04 19:45:11
@ ca76c778:e784c54b
2025-06-04 19:45:11A few days ago I remembered video by Antonio Stappaerts(Artwod) on Youtube. And I thought to myself I want to be really good at drawing hands.\ In the video he explains something that, in my opinion, applies when learning just about anything.
If you've heard of the Dunning-Kruger effect then you know the first part.\ If you haven't, one begins learning something and on top of the first peak thinks oneself to be almost a master. And then one learns a little bit more and realizes how little skill one actually has.
 \
Now, what is really interesting is this. He points out that the second slope is made up of many smaller Dunning-Kruger effects. For example the effect will apply when learning: the basic shape of the figure, how to pose the figure, how draw the hands, the hair etc.
\
Now, what is really interesting is this. He points out that the second slope is made up of many smaller Dunning-Kruger effects. For example the effect will apply when learning: the basic shape of the figure, how to pose the figure, how draw the hands, the hair etc.So the way to climb the second hill is to understand and practice these smaller skills. And not just once or twice. You want to reach close to the second peak of each of the smaller skills.
And with that in mind I search for a good tutorial about drawing hands and got down to it(for the third time).
Step one was to learn pose and gesture using a grid shape.
https://cdn.satellite.earth/f55a9d1ef2fd687a9dce5ceee5e05a1b666c436509e264ddbac4d260b99e882a.jpg
https://cdn.satellite.earth/1b5524635c20ee4869f4860c982deea469cb87be7ad7b404e1777497b5a4fbd4.jpg
https://cdn.satellite.earth/35652251243ffd8c495b855c319d27da0c193ff2e951591f0a9f1b35aad39b29.jpg
https://cdn.satellite.earth/68f55979d102b4ebe55177842c6d9ab2ab30b95f926441429d977b47fae925c3.jpg
Step two. Practice the basic forms for the palm and fingers.\ I got carried away and drew some hands.
https://cdn.satellite.earth/48b400f72e35d078368149f00182cb58e606ddd16f6db4e7789c1431c28d44a0.jpg
Step three. learn the measurements.
https://cdn.satellite.earth/75c9b82da90ef50d17f698dd7b1eadc223b74a019a702a4617ed7d321646a87c.jpg
Step four. Understand the fingers.
https://cdn.satellite.earth/e33f9f3f9217bf5e3e206e96dfe764eba09b9fb3c10b450bb9c8a4075e3c1ec8.jpg
Step five. Learn about the thumb and put it all together. Drawing from reference and imagination.
https://cdn.satellite.earth/b2dd9c1cc1045dde021272199818b0db331e71a603c5900122aa850eb2d4148a.jpg
https://cdn.satellite.earth/8f5647ae9e148ad6217c106b5b69cf231384475e0a0eedf210bd149f75ade0b7.jpg
-
 @ a5ee4475:2ca75401
2025-06-04 14:31:23
@ a5ee4475:2ca75401
2025-06-04 14:31:23[EM ATUALIZAÇÃO]
vacina #saude #politica #manipulacao #mundial #genocidio #pandemia #conspiracao
Este artigo reúne algumas evidências mais antigas que vim registrando durante alguns anos contra a covid, vacinas obrigatórias e a ação de agências de governo, fundações, políticos, mídia tradicional, celebridades, influenciadores, cientistas, redes sociais e laboratórios, em envolvimento com genocídio e restrições de liberdades em escala mundial causado por decisões em várias esferas relativas ao covid e as vacinas obrigatórias em geral.
Porém, alguns links podem não estar mais disponiveis, foram que ainda faltam ser registradas muitas informações já divulgadas nos últimos anos e que não tivemos contato pela escassez de meios para a obtenção dessas informações de forma organizada. Portanto, o presente artigo ainda passará por atualizações de conteúdo e formatação, então se possível ajudem sugerindo com complementos ou alterações.
Explicações iniciais:
- Sars-Cov-2 é que é nome do vírus. Ele que causa a doença Covid-19;
- O Sars-Cov-2 é o segundo tipo de Sars-Cov documentado, o primeiro ocorreu em 2003;
- 'Coronavírus' na verdade é um nome genérico para vários vírus de gripes já comuns, dado para o tipo corona (com uma "coroa", 'espetos' ao redor dele), o Sars-Cov-2 é só uma delas.
1. Vacinas Obrigatórias em Geral
-
Vacinas e autismo em crianças https://publichealthpolicyjournal.com/vaccination-and-neurodevelopmental-disorders-a-study-of-nine-year-old-children-enrolled-in-medicaid/
-
O CDC admite que 98 milhões de pessoas receberam o vírus do câncer através da vacina da Poliomielite https://medicinanews.com.br/frente/frente_1/o-cdc-admite-que-98-milhoes-de-pessoas-receberam-o-virus-do-cancer-atraves-da-vacina-poliomielite/
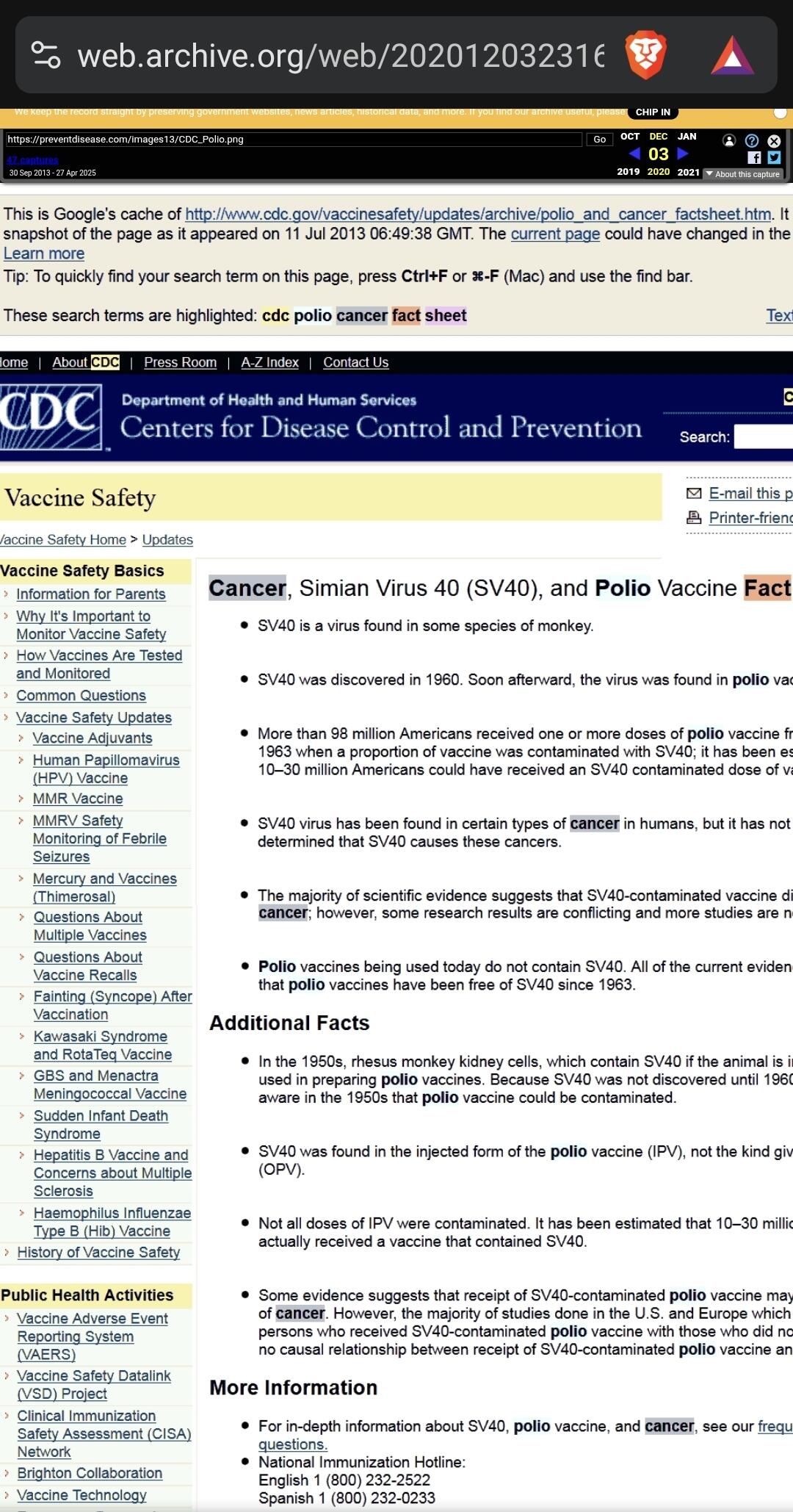 - Fonte original da imagem: https://preventdisease.com/images13/CDC_Polio.png [indisponível]
- Imagem arquivada em: https://web.archive.org/web/20201203231640/
- Fonte original da imagem: https://preventdisease.com/images13/CDC_Polio.png [indisponível]
- Imagem arquivada em: https://web.archive.org/web/20201203231640/"O CDC (Os Centros de Controle e Prevenção de Doenças dos Estados Unidos) removeu rapidamente uma página do seu site, que estava em cache no Google, como você pode ver logo abaixo, admitindo que mais de 98 milhões de americanos receberam uma ou mais doses de vacina contra pólio dentro de 8 período entre 1955 e 1963, quando uma proporção da vacina foi contaminada com um poliomavírus causador de câncer chamado SV40."
27/02/2021 - Por que o Japão demorou para vacinar, mesmo com Olimpíada se aproximando https://www.cnnbrasil.com.br/internacional/2021/02/27/por-que-o-japao-demorou-para-vacinar-mesmo-com-olimpiada-se-aproximando
"Desconfiança da população japonesa em relação a vacinas, ligada a casos ocorridos no passado, está entre razões que atrasaram imunização no país.
A resistência à vacina do Japão remonta à década de 1970, quando duas crianças morreram dentro de 24 horas após receberem a vacina combinada contra difteria, tétano e coqueluche (coqueluche). A vacina foi temporariamente suspensa, mas a confiança já havia sido abalada. Por vários anos, as taxas de vacinação infantil caíram, levando a um aumento nos casos de tosse convulsa.
No final dos anos 1980, houve outro susto com a introdução da vacina tripla contra sarampo, caxumba e rubéola produzida no Japão. As primeiras versões do imunizante foram associadas à meningite asséptica, ou inchaço das membranas ao redor do cérebro e da medula espinhal. O problema foi rastreado até o componente caxumba da vacina tripla, o que levou a uma ação judicial e a indenização por danos pesados.
O Instituto Nacional de Ciências da Saúde interrompeu a dose combinada em 1993 e a substituiu por vacinas individuais. Após o escândalo, Shibuya disse que o governo japonês se tornou "ciente dos riscos" e seu programa nacional de vacinação tornou-se voluntário.
O Dr. Yuho Horikoshi, especialista em doenças infecciosas, diz que os processos levaram a uma "lacuna de vacinação", em que nenhuma vacina foi aprovada no Japão por cerca de 15 anos.
Mais recentemente, em 2013, o Japão adicionou a vacina contra o papilomavírus humano (HPV) ao calendário nacional para proteger as meninas contra o vírus sexualmente transmissível, que é conhecido por causar câncer cervical. No entanto, vídeos de meninas supostamente sofrendo de reações adversas começaram a circular no YouTube, levando o governo a retirá-los da programação nacional."
2. PRIMEIRAS OCORRÊNCIAS PREDITIVAS AO COVID-19
2010 - Fundação Rockfeller, Lockstep. https://www.rockefellerfoundation.org/wp-content/uploads/Annual-Report-2010-1.pdf
Neste PDF da fundação Rockfeller, em seu próprio site, a fundação deixou claro o seu envolvimento em casos de ‘contenção’ de pandemias juntamente com a USAID (agência americana com nome ambíguo, como formalmente ‘United States Agency for International Development’, mas soando como ‘US Socorre’, mas sendo um braço do governo democrata que financiava interferências políticas diretas em vários países, como no Brasil: https://www.gazetadopovo.com.br/vida-e-cidadania/quais-ongs-cooperaram-com-moraes-e-sao-alvo-do-congresso-nos-eua/ ), inclusive em relacionadas ao SARS, um vírus muito semelhante ao SEGUNDO tipo de vírus Sars-Cov, o Sars-Cov-2 (o vírus propagado em 2019) e que causa o COVID-19.
Segundo eles:
“Integração entre Regiões e Países
A Fundação Rockefeler investiu US$ 22 milhões em sua Iniciativa de Redes de Vigilância de Doenças para ajudar a conter a disseminação de doenças infecciosas e pandemias, fortalecendo os sistemas nacionais, regionais e globais de vigilância e resposta a doenças. Dois programas-chave da Rockefeler — a Rede de Vigilância de Doenças da Bacia do Mekong e a Rede Integrada de Vigilância de Doenças da África Oriental — conectaram e capacitaram profissionais de saúde, epidemiologistas e autoridades de saúde pública em toda a região, levando a um aumento de seis vezes nos locais de vigilância de doenças transfronteiriças somente nos últimos três anos. Em 2010, a Rockefeler expandiu a bem-sucedida campanha transdisciplinar One Health, que a USAID e o Banco Asiático de Desenvolvimento adotaram como modelos. One Health refere-se à integração da ciência médica e veterinária para combater essas novas variedades de doenças zoonóticas que se movem e sofrem mutações rapidamente de animais para humanos. Essas colaborações criaram e fortaleceram uma rede regional crítica de saúde pública, enquanto as lições aprendidas foram exportadas entre disciplinas e países. Além de fortalecer os laços globais em saúde pública, a Rockefeler ajudou a elevar o nível de especialização e treinamento em campo. O Programa de Treinamento em Epidemiologia de Campo coloca graduados nos mais altos escalões do governo no Laos e no Vietnã, enquanto as bolsas da Rockefeler transformaram as ferramentas disponíveis para os médicos, permitindo-lhes utilizar o poder da internet para se comunicar e monitorar eventos, compreender contextos locais e analisar novos problemas. Finalmente, estamos aplicando ferramentas do século XXI para combater os desafios de saúde do século XXI.”
Julho de 2012 - Revista Mundo Estranho
Houve uma "coincidência", a revista Mundo Estranho em julho de 2012, entrevistou o até então doutorando em virologia, Átila Iamarino (o mesmo cientista que fez diversas propagandas das vacinas no Brasil), para descrever um possível cenário de propagação de uma epidemia viral, a revista descreve com grande precisão os eventos de 2020, mas apontando o oposto da China, em que, na realidade, sua economia cresceu vertiginosamente.
3. PRIMEIROS INDÍCIOS
10/2019 - Evento 201 - Durante os Jogos Militares Internacionais na China https://www.centerforhealthsecurity.org/event201/
Promovido por: - Bill & Melinda Gates Foundation - John Hopkins Institute - Fórum econômico mundial
"O evento simula a liberação de um coronavírus novo do tipo zoonótico transmitido por morcegos para porcos e por fim para humanos. Eventualmente ele se torna muito transmissível entre humanos levando a uma pandemia severa. O vírus é muito parecido com o vírus da SARS, mas se transmite muito mais facilmente entre pessoas devido a sintomas muito mais leves destas."
Também mencionado por: [Jornal Estadão] ( http://patrocinados.estadao.com.br/medialab/releaseonline/releasegeral-releasegeral/geral-johns-hopkins-center-for-health-security-forum-economico-mundial-e-fundacao-bill-melinda-gates-realizam-exercicio-pandemico-e-transmissao-ao-vivo/)
Sobre o "Movimento antivacina"
05/12/2017 - Movimento antivacina: como surgiu e quais consequências ele pode trazer? https://www.uol.com.br/universa/noticias/redacao/2017/12/05/o-que-o-movimento-antivacina-pode-causar.htm?cmpid=copiaecola
23/03/2019 - "Instagram bloqueia hashtags e conteúdo antivacinação" https://canaltech.com.br/redes-sociais/instagram-bloqueia-hashtags-e-conteudo-antivacinacao-135411/
23/05/2021 - Novos dados sobre pesquisadores de Wuhan aumentam debate sobre origens da Covid https://www.cnnbrasil.com.br/saude/novos-dados-sobre-pesquisadores-de-wuhan-aumentam-debate-sobre-origens-da-covid/
"A China relatou à Organização Mundial da Saúde que o primeiro paciente com sintomas semelhantes aos de Covid-19 foi registrado em Wuhan em 8 de dezembro de 2019"
01/02/2020 - O que aconteceu desde que o novo coronavírus foi descoberto na China https://exame.com/ciencia/o-que-aconteceu-desde-que-o-novo-coronavirus-foi-descoberto-na-china/
"O primeiro alerta foi recebido pela Organização Mundial da Saúde (OMS) em 31 de dezembro de 2019"
15/09/2020 - YouTube diz que vai remover vídeos com mentiras sobre vacina contra COVID-19 https://gizmodo.uol.com.br/youtube-remover-videos-mentiras-vacina-covid-19/
"O YouTube anunciou na quarta-feira (14) que estenderá as regras atuais sobre mentiras, propaganda e teorias da conspiração sobre a pandemia do coronavírus para incluir desinformação sobre as vacinas contra a doença.
De acordo com a Reuters, a gigante do vídeo diz que agora vai proibir conteúdos sobre vacinas contra o coronavírus que contradizem “o consenso de especialistas das autoridades de saúde locais ou da OMS”, como afirmações falsas de que a vacina é um pretexto para colocar chips de rastreamento nas pessoas ou que irá matar ou esterilizar quem tomar."
*07/01/2021 - YouTube vai punir canais que promovem mentiras sobre eleições – incluindo os de Trump https://olhardigital.com.br/2021/01/07/noticias/youtube-vai-punir-canais-que-promovem-mentiras-sobre-eleicoes-incluindo-os-de-trump/
"O YouTube anunciou que vai punir canais que promovem mentiras sobre as eleições, removendo sumariamente qualquer vídeo que contenha desinformação e, ao mesmo tempo, advertindo com um “strike” o canal que o veicular. A medida já está valendo e a primeira “vítima” é ninguém menos que o ex-presidente americano, Donald Trump.
A medida não é exatamente nova, mas foi novamente comunicada e reforçada pelo YouTube na quarta-feira (6), após os eventos de invasão do Capitólio, em Washington, onde o presidente eleito Joe Biden participava da cerimônia que confirmava a sua vitória nas eleições de novembro de 2020. A ocasião ficou marcada pela tentativa de invasão de correligionários de Trump, que entraram no edifício em oposição à nomeação do novo presidente. Uma mulher acabou sendo morta pela polícia que protegia o local.
O ex-presidente Donald Trump teve vídeos banidos de seu canal no YouTube após os eventos de ontem (6) no capitólio."
4. FIGURAS CENTRAIS
Bill Gates
- Bill Gates diz 'não' a abrir patentes de vacinas https://www.frontliner.com.br/bill-gates-diz-nao-a-abrir-patentes-de-vacinas/
"Bill Gates, um dos homens mais ricos do mundo, cuja fundação tem participação na farmacêutica alemã CureVac, produtora de vacina mRNA para prevenção de covid-19, disse não acreditar que a propriedade intelectual tenha algo a ver com o longo esforço global para controlar a pandemia."
João Doria e São Paulo
26/07/2017 - João Dória vai a China conhecer drones para ampliar segurança eletrônica na capital paulista https://jc.ne10.uol.com.br/blogs/jamildo/2017/07/26/joao-doria-vai-china-conhecer-drones-para-ampliar-seguranca-eletronica-na-capital-paulista/
02/08/2019 - Governo de SP fará Missão China para ampliar cooperação e atrair investimentos https://www.saopaulo.sp.gov.br/spnoticias/governo-de-sao-paulo-detalha-objetivos-da-missao-china/
20/11/2019 - Doria se encontra com chineses das gigantes CREC e CRCC e oferece concessões de rodovia, metrô e ferrovia https://diariodotransporte.com.br/2019/11/20/doria-se-encontra-com-chineses-das-gigantes-crec-e-crcc-e-oferece-concessoes-de-rodovia-metro-e-ferrovia/
25/01/2020 - "Chineses serão agressivos" nas privatizações em SP até 2022, afirma Dória https://noticias.uol.com.br/colunas/jamil-chade/2020/01/25/entrevista-joao-doria-privatizacoes-sao-paulo-china.htm
O governador de São Paulo, João Doria, afirma que vai acelerar os programas de desestatização no estado em 2020 e acredita que concessões e vendas poderão permitir uma arrecadação de pelo menos R$ 40 bilhões. Nesse processo, o governador avalia que a China deve atuar de forma agressiva e que aprofundará sua posição de maior parceira comercial do estado, se distanciando de americanos e argentinos.
29/06/2020 - Doria estabelece multa para quem estiver sem máscara na rua em SP https://veja.abril.com.br/saude/doria-estabelece-multa-para-quem-estiver-sem-mascara-na-rua/
24/12/2020 - Doria é flagrado sem máscara e fazendo compras em Miami https://pleno.news/brasil/politica-nacional/doria-e-flagrado-sem-mascara-e-fazendo-compras-em-miami.html
"Foto do governador de São Paulo sem o item de proteção viralizou nas redes"
07/06/2021 - Doria é criticado na internet por tomar sol sem máscara em hotel no Rio https://vejasp.abril.com.br/cidades/doria-e-criticado-na-internet-por-tomar-sol-sem-mascara-em-hotel-no-rio/
30/09/2020 - Governo de SP assina contrato com Sinovac e prevê vacina para dezembro https://agenciabrasil.ebc.com.br/saude/noticia/2020-09/governo-de-sp-assina-contrato-com-sinovac-e-preve-vacina-para-dezembro
O governador de São Paulo, João Doria, e o vice-presidente da laboratório chinês Sinovac, Weining Meng, assinaram hoje (30), um contrato que prevê o fornecimento de 46 milhões de doses da vacina CoronaVac para o governo paulista até dezembro deste ano.
O contrato também prevê a transferência tecnológica da vacina da Sinovac para o Instituto Butantan, o que significa que, o instituto brasileiro poderá começar a fabricar doses dessa vacina contra o novo coronavírus. O valor do contrato, segundo o governador João Doria é de US$ 90 milhões.
20/10/2020 - Coronavac terá mais de 90% de eficácia, afirmam integrantes do governo paulista https://www.cnnbrasil.com.br/saude/2020/12/20/coronavac-tera-mais-de-90-de-eficacia-afirmam-integrantes-do-governo
24/10/2020 - Não esperamos 90% de eficácia da Coronavac’, diz secretário de saúde de SP https://www.cnnbrasil.com.br/saude/2020/12/24/nao-esperamos-90-de-eficacia-da-coronavac-diz-secretario-de-saude-de-sp
07/01/2021 - Vacina do Butantan: eficácia é de 78% em casos leves e 100% em graves https://www.cnnbrasil.com.br/saude/2021/01/07/vacina-do-butantan-eficacia-e-de-78-em-casos-leves-e-100-em-graves
09/01/2021 - Não é hora de sermos tão cientistas como estamos sendo agora https://g1.globo.com/sp/sao-paulo/video/nao-e-hora-de-sermos-tao-cientistas-como-estamos-sendo-agora-diz-secretario-de-saude-de-sp-9166405.ghtml
10/01/2021 - Dados da Coronavac relatados à Anvisa não estão claros, diz médico https://www.cnnbrasil.com.br/saude/2021/01/10/dados-da-coronavac-relatados-a-anvisa-nao-estao-claros-diz-medico
"O diretor do Laboratório de Imunologia do Incor, Jorge Kalil, reforçou que faltaram informações sobre a Coronavac nos dados divulgados à Anvisa"
12/01/2021 - New Brazil data shows disappointing 50,4% efficacy for China’s Coronavac vaccine [Novos dados do Brasil mostram eficácia decepcionante de 50,4% para a vacina CoronaVac da China] https://www.reuters.com/article/us-health-coronavirus-brazil-coronavirus/new-brazil-data-shows-disappointing-504-efficacy-for-chinas-coronavac-vaccine-idUSKBN29H2CE
13/01/2021 - Eficácia da Coronavac: 50,38%, 78% ou 100%? https://blogs.oglobo.globo.com/lauro-jardim/post/5038-78-ou-100.html
“De acordo com interlocutores que participaram tanto do anúncio de ontem como da semana passada, quem pressionou para que os dados de 78% e 100% fossem liberados foi João Dória.”
07/05/2021 - Covid-19: Doria toma primeira dose da vacina CoronaVac https://veja.abril.com.br/saude/covid-19-doria-toma-primeira-dose-da-vacina-coronavac/
04/06/2021 - Doria é vacinado com a segunda dose da CoronaVac em São Paulo https://noticias.uol.com.br/politica/ultimas-noticias/2021/06/04/doria-e-vacinado-com-a-segunda-dose-da-coronavac-em-sao-paulo.htm
15/07/2021 - Doria testa positivo para a Covid-19 pela 2ª vez https://www.correiobraziliense.com.br/politica/2021/07/4937833-doria-testa-positivo-para-covid-19-pela-segunda-vez.html
"Governador de São Paulo já havia sido diagnosticado com a doença no ano passado. Ele diz que, apesar da infecção, se sente bem, o que atribui ao fato de ter sido vacinado com duas doses da Coronavac"
06/08/2021 - CPI recebe investigação contra Doria por compra de máscara sem licitação https://www.conexaopoder.com.br/nacional/cpi-recebe-investigacao-contra-doria-por-compra-de-mascara-sem-licitacao/150827
"Empresa teria usado o nome de Alexandre Frota para vender máscaras ao governo de SP. Doria nega informação"
Renan Filho
(filho do Renan Calheiros)
25/07/2019 - Governador Renan Filho vai à China em busca de investimentos para o estado https://www.tnh1.com.br/videos/vid/governador-renan-filho-vai-a-china-em-busca-de-investimentos-para-o-estado/
20/03/2020 - Governadores do NE consultam China e pedem material para tratar covid-19 https://noticias.uol.com.br/saude/ultimas-noticias/redacao/2020/03/20/governadores-do-ne-consultam-china-e-pedem-material-para-tratar-covid-19.htm
5. Narrativas, restrições e proibições
17/12/2020 - STF decide que vacina contra a covid pode ser obrigatória, mas não forçada https://noticias.uol.com.br/saude/ultimas-noticias/redacao/2020/12/17/stf-julga-vacinacao-obrigatoria.htm?cmpid=copiaecola
"O STF (Supremo Tribunal Federal) decidiu, em julgamento hoje, que o Estado pode determinar a obrigatoriedade da vacinação contra a covid-19. Porém fica proibido o uso da força para exigir a vacinação, ainda que possam ser aplicadas restrições a direitos de quem recusar a imunização.
Dez ministros foram favoráveis a obrigatoriedade da vacinação, que poderá ser determinada pelo governo federal, estados ou municípios. As penalidades a quem não cumprir a obrigação deverão ser definidas em lei."
27/07/2021 - Saiba que países estão adotando 'passaporte da vacina' para suspender restrições https://www.cnnbrasil.com.br/internacional/2021/07/27/saiba-que-paises-estao-adotando-passaporte-da-vacina-para-suspender-restricoes
" - Israel - Uniao Europeia - Áustria - Dinamarca - Eslovênia - França - Grécia - Irlanda - Itália - Letônia - Lituânia - Luxemburgo - Holanda - Portugal - Japão - Coreia do sul"
18/06/2021 - O que é o passaporte da vacina que Bolsonaro quer vetar? https://noticias.uol.com.br/politica/ultimas-noticias/2021/06/18/uol-explica-o-que-e-o-passaporte-da-vacina-que-opoe-bolsonaro-e-damares.htm
"O Brasil poderá ter um certificado de imunização futuramente. Aprovado no Senado na semana passada, o "passaporte da vacina", como é chamado, prevê identificar pessoas vacinadas para que entrem em locais públicos ou privados com possíveis restrições."
6. Vacinas
Alegações iniciais
- CoronaVac, Oxford e Pfizer: veja diferenças entre as vacinas contra covid noticias.uol.com.br/saude/ultimas-noticias/redacao/2021/05/11/diferencas-vacinas-covid-brasil.htm
" - CoronaVac (Butantan/Sinovac - Chinesa) Com virus inativo 50,38% de eficácia 2 doses
-
Covishield - 'AstraZeneca' (Fiocruz/Astrazenica/Oxford - Britânica) Com virus não replicante 67% de eficácia 2 doses
-
ComiRNAty - 'Pfizer' (Pfizer - Americana / BioNTech - Alemã) Com RNA mensageiro 96% de eficácia 2 doses"
Riscos diretos
15/06/2021 - Trombose após vacinação com AstraZeneca: Quais os sintomas e como se deve atuar? https://www.istoedinheiro.com.br/trombose-apos-vacinacao-com-astrazeneca-quais-os-sintomas-e-como-se-deve-atuar/
"Agências europeias estão reticentes com a vacina da AstraZeneca. Ela chegou a ser desaconselhada a pessoas com idade inferior a 60 anos, e um alto funcionário da Agência Europeia de Medicamentos declarou que era melhor deixar de administrar a vacina deste laboratório em qualquer idade quando há alternativas disponíveis, devido aos relatos de trombose após a primeira dose, apesar de raros."
11/05/2021 - CoronaVac, Oxford e Pfizer: veja diferenças entre as vacinas contra covid https://noticias.uol.com.br/saude/ultimas-noticias/redacao/2021/05/11/diferencas-vacinas-covid-brasil.htm
"Na terça-feira (12), o Ministério da Saúde determinou a suspensão da aplicação da vacina de Oxford/AstraZeneca para gestantes e puérperas com comorbidades. A decisão segue recomendação da Anvisa, que apura a morte de uma grávida de 35 anos que tomou o imunizante e teve um AVC (acidente vascular cerebral)."
30/07/2021 - Pfizer representa o mesmo risco de trombose que a Astrazeneca, aponta levantamento https://panoramafarmaceutico.com.br/pfizer-representa-o-mesmo-risco-de-trombose-que-a-astrazeneca-aponta-levantamento/
7. CRIMES
Crimes da Pfizer
18/11/2020 Não listado no google - Os Crimes documentados da produtora de vacinas de Covid - Pfizer [INGLÊS] https://www.dmlawfirm.com/crimes-of-covid-vaccine-maker-pfizer-well-documented/
"A velocidade com que a vacina Covid da Pfizer foi produzida, a ausência de estudos em animais, testes de controle randomizados e outros testes e procedimentos padrão usuais para um novo medicamento são, no mínimo, preocupantes. Além disso, todos os fabricantes de vacinas Covid receberam imunidade legal para quaisquer ferimentos ou mortes que possam causar. Se essas vacinas são tão seguras quanto promovidas, por que seus fabricantes precisam de imunidade geral?"
"A Pfizer, uma empresa farmacêutica que parece ter ganhado na loteria para produzir a primeira vacina Covid-19, está atualmente lutando contra centenas de ações judiciais sobre o Zantac, um popular medicamento contra azia. Os processos da Zantac afirmam que a droga popular pode estar contaminada com uma substância cancerígena chamada N-nitrosodimetilamina (NDMA). Os processos Zantac são em aberto e em andamento, já que a farmacêutica está lutando contra eles; mas a Pfizer, sabemos, cometeu vários crimes ou transgressões pelos quais foi punida nos últimos anos. As falhas da empresa estão bem documentadas e vale a pena revisá-las neste momento crítico da história da humanidade, enquanto todos nós buscamos respostas."
A Pfizer recebeu a maior multa da história dos Estados Unidos como parte de um acordo judicial de US $ 2,3 bilhões com promotores federais por promover medicamentos erroneamente (Bextra, Celebrex) e pagar propinas a médicos complacentes. A Pfizer se confessou culpada de falsificar a marca do analgésico Bextra, promovendo o medicamento para usos para os quais não foi aprovado.
Na década de 1990, a Pfizer estava envolvida em válvulas cardíacas defeituosas que causaram a morte de mais de 100 pessoas. A Pfizer enganou deliberadamente os reguladores sobre os perigos. A empresa concordou em pagar US $ 10,75 milhões para acertar as acusações do departamento de justiça por enganar reguladores.
A Pfizer pagou mais de US $ 60 milhões para resolver um processo sobre o Rezulin, um medicamento para diabetes que causou a morte de pacientes de insuficiência hepática aguda.
No Reino Unido, a Pfizer foi multada em quase € 90 milhões por sobrecarregar o NHS, o Serviço Nacional de Saúde. A Pfizer cobrou do contribuinte um adicional de € 48 milhões por ano, pelo que deveria custar € 2 milhões por ano.
A Pfizer concordou em pagar US $ 430 milhões em 2004 para resolver acusações criminais de que havia subornado médicos para prescrever seu medicamento para epilepsia Neurontin para indicações para as quais não foi aprovado. Em 2011, um júri concluiu que a Pfizer cometeu fraude em sua comercialização do medicamento Neurontin. A Pfizer concordou em pagar $ 142,1 milhões para liquidar as despesas.
A Pfizer revelou que pagou quase 4.500 médicos e outros profissionais médicos cerca de US $ 20 milhões por falar em nome da Pfizer.
Em 2012, a Comissão de Valores Mobiliários dos Estados Unidos - anunciou que havia chegado a um acordo de US $ 45 milhões com a Pfizer para resolver acusações de que suas subsidiárias haviam subornado médicos e outros profissionais de saúde no exterior para aumentar as vendas no exterior.
A Pfizer foi processada em um tribunal federal dos Estados Unidos por usar crianças nigerianas como cobaias humanas, sem o consentimento dos pais das crianças. A Pfizer pagou US $ 75 milhões para entrar em acordo no tribunal nigeriano pelo uso de um antibiótico experimental, o Trovan, nas crianças. A empresa pagou um valor adicional não divulgado nos Estados Unidos para liquidar as despesas aqui. A Pfizer violou o direito internacional, incluindo a Convenção de Nuremberg estabelecida após a Segunda Guerra Mundial, devido aos experimentos nazistas em prisioneiros relutantes.
Em meio a críticas generalizadas de roubar os países pobres em busca de drogas, a Pfizer prometeu dar US $ 50 milhões para um medicamento para a AIDS para a África do Sul. Mais tarde, no entanto, a Pfizer falhou em honrar essa promessa.
- Pfizer contract leaked!
[Contrato da Pfizer vazado]
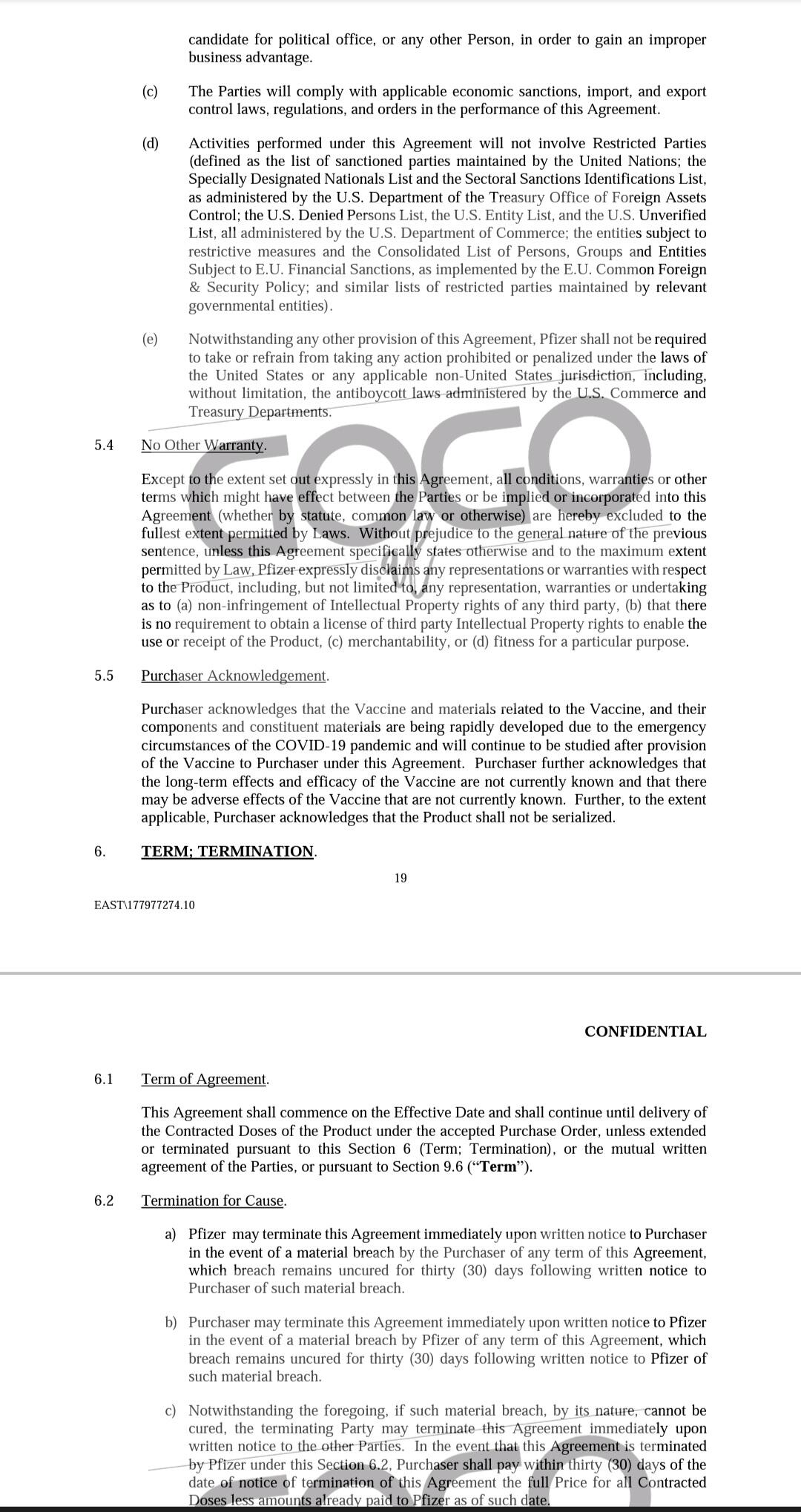 http://sanjeev.sabhlokcity.com/Misc/LEXO-KONTRATEN-E-PLOTE.pdf
http://sanjeev.sabhlokcity.com/Misc/LEXO-KONTRATEN-E-PLOTE.pdf
Segundo o contrato "o produto não deve ser serializado":
"5.5 Reconhecimento do comprador.
O Comprador reconhece que a Vacina e os materiais relacionados à Vacina, e seus componentes e materiais constituintes estão sendo desenvolvidos rapidamente devido às circunstâncias de emergência da pandemia de COVID-19 e continuarão a ser estudados após o fornecimento da Vacina ao Comprador nos termos deste Contrato. O Comprador reconhece ainda que os efeitos de longo prazo e eficácia da Vacina não são atualmente conhecidos e que pode haver efeitos adversos da Vacina que não são atualmente conhecidos. Além disso, na medida do aplicável, o Comprador reconhece que o Produto não deve ser serializado."
Crimes da AstraZeneca
21/06/2003 - AstraZeneca se declara culpada no esquema de médico de câncer https://www.nytimes.com/2003/06/21/business/astrazeneca-pleads-guilty-in-cancer-medicine-scheme.html
"A AstraZeneca, a grande empresa farmacêutica, se declarou culpada hoje de uma acusação de crime de fraude no sistema de saúde e concordou em pagar $ 355 milhões para resolver as acusações criminais e civis de que se envolveu em um esquema nacional para comercializar ilegalmente um medicamento contra o câncer de próstata.
O governo disse que os funcionários da empresa deram incentivos financeiros ilegais a cerca de 400 médicos em todo o país para persuadi-los a prescrever o medicamento Zoladex. Esses incentivos incluíram milhares de amostras grátis de Zoladex [...]"
27/04/2010 - Farmacêutica gigante AstraZeneca pagará US $ 520 milhões pelo marketing de medicamentos off-label https://www.justice.gov/opa/pr/pharmaceutical-giant-astrazeneca-pay-520-million-label-drug-marketing
"AstraZeneca LP e AstraZeneca Pharmaceuticals LP vão pagar $ 520 milhões para resolver as alegações de que a AstraZeneca comercializou ilegalmente o medicamento antipsicótico Seroquel para usos não aprovados como seguros e eficazes pela Food and Drug Administration (FDA), os Departamentos de Justiça e Saúde e Serviços Humanos A Equipe de Ação de Fiscalização de Fraudes em Saúde (HEAT) anunciou hoje. Esses usos não aprovados também são conhecidos como usos "off-label" porque não estão incluídos no rótulo do medicamento aprovado pela FDA."
- List of largest pharmaceutical settlements [Lista dos maiores acordos farmaceuticos] https://en.m.wikipedia.org/wiki/List_of_largest_pharmaceutical_settlements
8. CIENTISTAS
Especialistas Sérios
- Máscara Provoca Insuficiência Respiratória E Contaminação Microbiana… [Canal deletado] https://youtube.com/watch?v=eHu-pydSvDI
Não lembro mais a quem pertencia, mas provavelmente era de um médico falando do assunto. Creio ter sido do Dr. Paulo Sato, por essa temática ter sido abordada por ele, mas ao abrir o site aparece somente:
"Este vídeo foi removido por violar as diretrizes da comunidade do YouTube"
Dr. Paulo Sato
- USAR ou NÃO USAR a CUECA do seu governador no rosto https://fb.watch/7NPP_7rS5S/ https://www.facebook.com/AdoniasSoaresBR/videos/1347904292291481/ Adonias Soares entrevista ao Dr. Paulo Sato sobre as máscaras, em que é simulado o efeito da respiração prolongada das máscaras no organismo com o uso de águas de torneira, natural, gaseificada (com gás carbônico) e antioxidante, em que a com gás carbônico (PH 4 - Ácido) representa o organismo humano, e na prática representa lesão corporal e iniciação de doenças.
Dr. Kary Mullis
(Criador do teste PCR)
- PCR nas palavras do seu inventor - Dr. Kary Mullis (legendado) https://www.youtube.com/watch?v=W1O52uTygk8
"Qualquer um pode testar positivo para quase qualquer coisa com um teste de PCR, se você executá-lo por tempo suficiente… Com PCR, se voce fizer isso bem, você pode encontrar quase tudo em qualquer pessoa… Isso não te diz que você está doente."
- Kary Mullis DESTRUYE a Anthony Fauci lbry://@CapitalistChile#0/Kary-Mullis---Fauci#5
"Ele [...] não entende de medicina e não deveria estar onde está. A maioria dos que estão acima são só administrativos e não têm nem ideia do que ocorre aqui em baixo e essas pessoas tem uma agenda que não é a que gostaríamos que tivessem, dado que somos nós os que pagamos a eles para que cuidem da nossa saúde. Têm uma agenda pessoal."
Dra. Li-Meng Yan
- Dra. Li-Meng Yan: O vírus foi criado em laboratório com um objetivo: Causar dano. https://youtu.be/pSXp3CZnvOc
Dr. Joe Roseman
- Cientista Phd Dr Joe Roseman faz seríssimas advertencias sobre a picada https://youtu.be/0PIXVFqJ_h8
Dr. Robert Malone
- As vacinas podem estar causando ADE - Dr. Robert Malone https://odysee.com/@AkashaComunidad:f/Las_vacunas_pueden_estar_causando_ADE_magnificaci%C3%B3n_mediada_por:f lbry://@Información.#b/Drrm#9
Dr. Robert Malone, um dos três inventores da tecnologia de RNAm que se usa de forma farmacêutica. No vídeo fala sobre os efeitos de ADE (realce dependente de anticorpos) que estão ocorrendo com as vacinas. Nas palavras do Dr. Malone, já não é somente uma hipótese, mas baseada nos conhecimentos gerados nas provas e ensaios pré clínicos, com as vacinas contra o primeiro vírus da SARS.
Dr. Luc Montagnier
- Dr. Luc Montagnier, virologista, prêmio Nobel de medicina, um dos descobridores do vírus HIV, afirma: "a vacinação em massa está criando as novas variantes' (@medicospelavida , telegram)
Falsos Especialistas
-
Dr. Anthony Fauci - Imunologista
-
Dr. Atila Iamarino (nerdologia) - Microbiólogo
Atualmente propagandeia a pauta climática do COP30 (30th Conference Of Parties - UN [30ª Conferência das Partes - ONU]) que será no Brasil.
9. CASOS DOCUMENTADOS
13 de setembro de 2021 - 13/09/2021 - Carta aberta ao Ministro da Saúde por Arlene Ferrari Graf, mãe de Bruno Oscar Graf https://telegra.ph/Carta-aberta-ao-Ministro-da-Sa%C3%BAde-09-13
Também em: Gazeta do Povo
O texto de uma mãe discorrendo sobre o filho dela, Bruno Oscar Graf, ter ANTI-HEPARINA PF4 AUTO-IMUNE e ter vindo a falecer por reação à vacina.
11/05/2021 - Rio notifica morte de grávida vacinada com imunizante Oxford https://www.terra.com.br/noticias/coronavirus/rio-notifica-morte-de-gravida-vacinada-com-imunizante-oxford,415b9b0c49169427ac2f90ae3765c057e9suy3qn.html
"Vítima não apresentava histórico de doença circulatória nem sofria de nenhuma doença viral; relação será investigada"
13/08/2021 - Cruzeiro com 4.336 pessoas tem 27 contaminados com Covid-19 em Belize https://paranaportal.uol.com.br/geral/cruzeiro-com-4-336-pessoas-tem-27-contaminados-com-covid-19-em-belize/amp/
"Segundo um comunicado do Conselho de Turismo de Belize emitido na quarta-feira (11), 26 contaminados são da tripulação e um é passageiro. A maioria é assintomática e os 27 estão vacinados."
10. ALEGAÇÕES DIRETAS
Setembro de 2021 - 09/2021 - BOMBA: Ex-membro do Partido Comunista da China revela que o primeiro surto da Covid foi “intencional” https://terrabrasilnoticias.com/2021/09/bomba-ex-membro-do-partido-comunista-da-china-revela-que-o-primeiro-surto-da-covid-foi-intencional/
-
 @ 6ad3e2a3:c90b7740
2025-06-04 08:32:29
@ 6ad3e2a3:c90b7740
2025-06-04 08:32:29"Modern science is based on this principle: give us one free miracle and then we'll explain the rest."
— Terrence McKenna
I always wondered why a pot of water boils on the stove. I mean I know it boils because I turned on the electricity, but why does the electricity cause it to boil? I know the electricity produces heat, and the heat is conducted through the stainless steel pot and into the water, but why does the heat transfer from stovetop to the water?
I know the heat from the stove via the pot speeds up the molecules in the water touching it and that they in turn speed up the molecules touching them and so on throughout the pot, but why do speedy molecules cause adjacent molecules to speed up?
I mean I know they do this, but why do they do this? Why couldn’t it be that sped-up molecules only interact with sufficient speedy molecules and ignore slower ones? Why do they interact with all the molecules, causing all of them to speed up? Or why don’t the speedy ones, instead of sharing their excited state, hoard it and take more energy from adjacent slower molecules, thereby making them colder, i.e., why doesn’t half the water boil twice as fast (on the left side of the pot) while the other half (right side) turns to ice?
The molecules tend to bounce around randomly, interacting as equal opportunists on the surrounding ones rather than distinguishing only certain ones with which to interact. Why do the laws of thermodynamics behave as such rather than some other way?
There may be yet deeper layers to this, explanations going down to the atomic and even quantum levels, but no matter how far you take them, you are always, in the end, left with: “Because those are the laws of physics”, i.e., “because that’s just how it is.”
. . .
The Terrence McKenna quote, recently cited by Joe Rogan on his podcast, refers to the Big Bang, the current explanation adopted by the scientifically literate as to the origins of the universe. You see there was this insanely dense, infinitesimally small micro dot that one day (before the dawn of time) exploded outward with unimaginable power that over billions of years created what we perceive as the known universe.
What happened prior? Can’t really say because time didn’t yet exist, and “prior” doesn’t make sense in that context. Why did it do this? We don’t know. How did it get there? Maybe a supermassive black hole from another universe got too dense and exploded out the other side? Highly speculative.
So why do people believe in the Big Bang? Because it comports with and explains certain observable phenomena and predicted other phenomena which were subsequently confirmed. But scratch a little deeper for an explanation as to what caused it, for what purpose did it occur or what preceded it, and you hit the same wall.
. . .
Even if we were to understand at a quantum level how and why the Big Bang happened and what preceded it, let’s assume it’s due to Factor X, something we eventually replicated with mini big-bangs and universe creations in our labs, we would still be tasked with understanding why Factor X exists in the universe. And if Factor X were explained by Process Y, we’d still be stuck needing an explanation for Process Y — ad infinitum.
Science can thus only push the wall back farther, but can never scale it. We can never arrive at an ultimate explanation, only partial ones. Its limitations are the limitations of thought itself, the impossibility of ever creating a map at a scale of one mile per mile.
-
 @ b1ddb4d7:471244e7
2025-06-04 07:01:24
@ b1ddb4d7:471244e7
2025-06-04 07:01:24Bitcoin FilmFest (BFF25) returns to Warsaw for its third edition, blending independent cinema—from feature films and commercials to AI-driven experimental visuals—with education and entertainment.
Hundreds of attendees from around the world will gather for three days of screenings, discussions, workshops, and networking at the iconic Kinoteka Cinema (PKiN), the same venue that hosted the festival’s first two editions in March 2023 and April 2024.
This year’s festival, themed “Beyond the Frame,” introduces new dimensions to its program, including an extra day on May 22 to celebrate Bitcoin Pizza Day, the first real-world bitcoin transaction, with what promises to be one of Europe’s largest commemorations of this milestone.
BFF25 bridges independent film, culture, and technology, with a bold focus on decentralized storytelling and creative expression. As a community-driven cultural experience with a slightly rebellious spirit, Bitcoin FilmFest goes beyond movies, yet cinema remains at its heart.
Here’s a sneak peek at the lineup, specially curated for movie buffs:
 Generative Cinema – A special slot with exclusive shorts and a thematic debate on the intersection of AI and filmmaking. Featured titles include, for example: BREAK FREE, SATOSHI: THE CREATION OF BITCOIN, STRANGE CURRENCIES, and BITCOIN IS THE MYCELIUM OF MONEY, exploring financial independence, traps of the fiat system, and a better future built on sound money.
Generative Cinema – A special slot with exclusive shorts and a thematic debate on the intersection of AI and filmmaking. Featured titles include, for example: BREAK FREE, SATOSHI: THE CREATION OF BITCOIN, STRANGE CURRENCIES, and BITCOIN IS THE MYCELIUM OF MONEY, exploring financial independence, traps of the fiat system, and a better future built on sound money. Upcoming Productions Preview – A bit over an hour-long block of unreleased pilots and works-in-progress. Attendees will get exclusive first looks at projects like FINDING HOME (a travel-meets-personal-journey series), PARALLEL SPACES (a story about alternative communities), and THE LEGEND OF LANDI (a mysterious narrative).
Upcoming Productions Preview – A bit over an hour-long block of unreleased pilots and works-in-progress. Attendees will get exclusive first looks at projects like FINDING HOME (a travel-meets-personal-journey series), PARALLEL SPACES (a story about alternative communities), and THE LEGEND OF LANDI (a mysterious narrative). Freedom-Focused Ads & Campaigns – Unique screenings of video commercials, animations, and visual projects, culminating in “The PoWies” (Proof of Work-ies)—the first ever awards show honoring the best Bitcoin-only awareness campaigns.
Freedom-Focused Ads & Campaigns – Unique screenings of video commercials, animations, and visual projects, culminating in “The PoWies” (Proof of Work-ies)—the first ever awards show honoring the best Bitcoin-only awareness campaigns.To get an idea of what might come up at the event, here, you can preview 6 selected ads combined into two 2 videos:
 Open Pitch Competition – A chance for filmmakers to present fresh ideas and unfinished projects to an audience of a dedicated jury, movie fans and potential collaborators. This competitive block isn’t just entertaining—it’s a real opportunity for creators to secure funding and partnerships.
Open Pitch Competition – A chance for filmmakers to present fresh ideas and unfinished projects to an audience of a dedicated jury, movie fans and potential collaborators. This competitive block isn’t just entertaining—it’s a real opportunity for creators to secure funding and partnerships. Golden Rabbit Awards: A lively gala honoring films from the festival’s Official Selection, with awards in categories like Best Feature, Best Story, Best Short, and Audience Choice.
Golden Rabbit Awards: A lively gala honoring films from the festival’s Official Selection, with awards in categories like Best Feature, Best Story, Best Short, and Audience Choice.BFF25 Main Screenings
Sample titles from BFF25’s Official Selection:
 REVOLUCIÓN BITCOIN – A documentary by Juan Pablo, making its first screening outside the Spanish-speaking world in Warsaw this May. Three years of important work, 80 powerful minutes to experience. The film explores Bitcoin’s impact across Argentina, Colombia, Mexico, El Salvador, and Spain through around 40 diverse perspectives. Screening in Spanish with English subtitles, followed by a Q&A with the director.
REVOLUCIÓN BITCOIN – A documentary by Juan Pablo, making its first screening outside the Spanish-speaking world in Warsaw this May. Three years of important work, 80 powerful minutes to experience. The film explores Bitcoin’s impact across Argentina, Colombia, Mexico, El Salvador, and Spain through around 40 diverse perspectives. Screening in Spanish with English subtitles, followed by a Q&A with the director. UNBANKABLE – Luke Willms’ directorial debut, drawing from his multicultural roots and his father’s pioneering HIV/AIDS research. An investigative documentary based on Luke’s journeys through seven African countries, diving into financial experiments and innovations—from mobile money and digital lending to Bitcoin—raising smart questions and offering potential lessons for the West. Its May appearance at BFF25 marks its largest European event to date, following festival screenings and nominations across multiple continents over the past year.
UNBANKABLE – Luke Willms’ directorial debut, drawing from his multicultural roots and his father’s pioneering HIV/AIDS research. An investigative documentary based on Luke’s journeys through seven African countries, diving into financial experiments and innovations—from mobile money and digital lending to Bitcoin—raising smart questions and offering potential lessons for the West. Its May appearance at BFF25 marks its largest European event to date, following festival screenings and nominations across multiple continents over the past year. HOTEL BITCOIN – A Spanish comedy directed by Manuel Sanabria and Carlos “Pocho” Villaverde. Four friends, 4,000 bitcoins , and one laptop spark a chaotic adventure of parties, love, crime, and a dash of madness. Exploring sound money, value, and relationships through a twisting plot. The film premiered at the Tarazona and Moncayo Comedy Film Festival in August 2024. Its Warsaw screening at BFF25 (in Spanish with English subtitles) marks its first public showing outside the Spanish-speaking world.
HOTEL BITCOIN – A Spanish comedy directed by Manuel Sanabria and Carlos “Pocho” Villaverde. Four friends, 4,000 bitcoins , and one laptop spark a chaotic adventure of parties, love, crime, and a dash of madness. Exploring sound money, value, and relationships through a twisting plot. The film premiered at the Tarazona and Moncayo Comedy Film Festival in August 2024. Its Warsaw screening at BFF25 (in Spanish with English subtitles) marks its first public showing outside the Spanish-speaking world.Check out trailers for this year’s BFF25 and past editions on YouTube.
Tickets & Info:
- Detailed program and tickets are available at bitcoinfilmfest.com/bff25.
- Stay updated via the festival’s official channels (links provided on the website).
- Use ‘LN-NEWS’ to get 10% of tickets
-
 @ 472f440f:5669301e
2025-06-04 01:37:37
@ 472f440f:5669301e
2025-06-04 01:37:37Marty's Bent
via nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqy0hwumn8ghj7mn0wd68yttjv4kxz7fwvf5hgcm0d9hzumnfde4xzqpq85h9z5yxn8uc7retm0n6gkm88358lejzparxms5kmy9epr236k2qtyz2zr
A lot of the focus over the last couple of months has been on the emergence of Strategy competitors in public markets looking to build sizable bitcoin treasuries and attract investors of all shapes and sizes to drive shareholder value. The other big topic in the bitcoin development world has been around OP_RETURN and the debate over whether or not the amount of data that can be shoved into a bitcoin transaction should be decided by the dominant implementation.
A topic that is just as, if not more, important that is not getting enough appreciation is the discussion around open source bitcoin developers and the lingering effects of the Biden administration's attack on Samourai Wallet and Tornado Cash. If you read our friend Matt Corallo's tweet above, you'll notice that the lingering effects are such that even though the Trump administration has made concerted efforts to reverse the effects of Operation Chokepoint 2.0 that were levied by the Biden administration, Elizabeth Warren, and her friends at the Treasury and SEC - it is imperative that we enshrine into law the rights of open source developers to build products and services that enable individuals to self-custody bitcoin and use it in a peer-to-peer fashion without the threat of getting thrown in jail cell.
As it stands today, the only assurances that we have are from an administration that is overtly in favor of the proliferation of bitcoin in the United States. There is nothing in place to stop the next administration or another down the line from reverting to Biden-era lawfare that puts thousands of bitcoin developers around the world at risk of being sent into a cage because the government doesn't like how some users leverage the code they write. To make sure that this isn't a problem down the line it is imperative that we pass the Blockchain Regulatory Clarity Act, which would not hold bitcoin developers liable for the ways in which end users leverage their tools.
Not only is this an act that would protect developers from pernicious government officials targeting them when end users use their technology in a way that doesn't make the government happy, it will also protect YOU, the end user, looking to transact in a peer-to-peer fashion and leverage all of the incredible properties of bitcoin the way they were meant to be. If the developers are not protected, they will not be able to build the technology that enables you to leverage bitcoin.
So do your part and go to saveourwallets.org. Reach out to your local representatives in Congress and Senators and make some noise. Let them know that this is something that you care deeply about and that they should not only pay attention to this bill but push it forward and enshrine it into law as quickly as possible.
There are currently many developers either behind bars or under house arrest for developing software that gives you the ability to use Bitcoin in a self-sovereign fashion and use it in a privacy-preserving way. Financial privacy isn't a crime. It is an inalienable human right that should be protected at all cost. The enshrinement of this inalienable right into law is way past due.
#FreeSamourai #FreeRoman
Headlines of the Day
MicroStrategy Copycats See Speculative Premiums Fade - via X
Square Tests Bitcoin Payments, Lightning Yields Beat DeFi - via X
Get our new STACK SATS hat - via tftcmerch.io
Bitfinex Moves $731M Bitcoin to Jack Mallers' Fund - via X
Take the First Step Off the Exchange
Bitkey is an easy, secure way to move your Bitcoin into self-custody. With simple setup and built-in recovery, it’s the perfect starting point for getting your coins off centralized platforms and into cold storage—no complexity, no middlemen.
Take control. Start with Bitkey.
Use the promo code “TFTC20” during checkout for 20% off
Ten31, the largest bitcoin-focused investor, has deployed $150.00M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/invest.
Final thought...
Should I join a country club?
Get this newsletter sent to your inbox daily: https://www.tftc.io/bitcoin-brief/
Subscribe to our YouTube channels and follow us on Nostr and X:
-
 @ 20e7c953:3b8bcb21
2025-06-05 10:45:07
@ 20e7c953:3b8bcb21
2025-06-05 10:45:0721… That number means something. A reminder that limits create value - both in Bitcoin and in life.
Every June 21st, skaters around the world remind us that freedom is something you make yourself - one push at a time only constrained by your own limitations.
This year in Vientiane, we’re proud to support one of the few real skate spots in Laos. A place built and held together by skaters for skaters.
Expect around 50 locals - from young kids to older heads - showing up not just to skate, but to hold space for each other. No ego, no filters, just boards, fun and respect.
Bitcoiners have lots to learn from these communities on this regard. Go skate and you'll find out.
SnF
Laostr
Skateboardingisfun
Skate4Fun
-
 @ da8b7de1:c0164aee
2025-06-05 17:39:41
@ da8b7de1:c0164aee
2025-06-05 17:39:41| Régió/Ország | Fő esemény/politika | Forrás | |------------------|--------------------------------------------------------------------------------------------------|-------------| | Egyesült Államok | Végrehajtási rendeletek a nukleáris termelés négyszeresére növeléséről; a nem létfontosságú K+F költségvetésének csökkentése; SMR és mikroreaktor kezdeményezések | world-nuclear-news, nucnet, aoshearman, ans | | Kanada | Engedélyezés új BWRX-300 SMR reaktor építésére Darlingtonban | world-nuclear-news, ans | | Európa | EU tervek az orosz nukleáris importok korlátozására; Westinghouse–Bulgária beszállítói megállapodások | nucnet, world-nuclear-news | | Globális/Világbank | A nukleáris finanszírozási tilalom esetleges feloldása a fejlődő országok számára | globalissues | | Egyesült Királyság| Új kiberbiztonsági jogszabályok a nukleáris szektorban | aoshearman | | Katonaság/Védelem| A védelmi minisztérium cégeket választott ki mikroreaktorok telepítésére | ans |
Források:
world-nuclear-news
nucnet
aoshearman
globalissues
ans -
 @ da8b7de1:c0164aee
2025-06-03 19:31:32
@ da8b7de1:c0164aee
2025-06-03 19:31:32Lengyelország előrelépése az első atomerőmű építésében
Lengyelország állami nukleáris vállalata, a Polskie Elektrownie Jadrowe (PEJ) és egy amerikai konzorcium – élén a Westinghouse és a Bechtel cégekkel – mérnöki fejlesztési megállapodást kötött. Ez a szerződés kulcsfontosságú lépés az ország első atomerőművének megvalósítása felé, lehetővé téve a részletes mérnöki és helyszínspecifikus munkák megkezdését. A lengyel kormány ezt mérföldkőnek tekinti az energiaszuverenitás és a dekarbonizáció felé vezető úton.
Amerikai politika: lendület az új nukleáris technológiáknak
Az Egyesült Államok kormánya elnöki rendeletet adott ki, amely reformokat vezet be a nukleáris reaktorok tesztelésében az Energiaügyi Minisztériumnál. A cél az új generációs reaktorok – köztük mikroreaktorok és kis moduláris reaktorok (SMR-ek) – fejlesztésének és engedélyezésének felgyorsítása, valamint a környezetvédelmi vizsgálatok egyszerűsítése. A rendelet legalább három új reaktor kritikus üzembe helyezését célozza meg 2026 júliusáig, támogatva ezzel az ipari alkalmazások széles körét, például adatközpontokat vagy hidrogéntermelést. Az intézkedés célja, hogy az USA visszaszerezze vezető szerepét a nukleáris innovációban, és csökkentse a korábbi években felhalmozódott engedélyezési akadályokat.
Kis moduláris reaktorok (SMR) fejlesztése világszerte
Az SMR-szektorban világszerte jelentős előrelépések történtek: - Az amerikai Tennessee Valley Authority (TVA) benyújtotta az első építési kérelmet egy GE Hitachi BWRX-300 SMR-re a Clinch River telephelyen. - Kanadában az Ontario Power Generation engedélyt kapott az első, négy tervezett SMR megépítésének megkezdésére a Darlington telephelyen. - Belgium és Brazília innovatív SMR-technológiákat vizsgál, köztük ólom-hűtésű reaktorokat és nemzetközi együttműködéseket. - Olyan technológiai óriások, mint a Google, az USA-ban korai fázisú fejlett nukleáris projektekbe fektetnek, ami a magánszektor növekvő érdeklődését mutatja.
Globális ipari és pénzügyi támogatás a nukleáris bővítéshez
Széles körű koalíció – köztük olyan nagyvállalatok, mint az Amazon, Google, Meta, Dow – és pénzügyi intézmények kötelezték el magukat amellett, hogy 2050-re megháromszorozzák a globális nukleáris kapacitást. Ez összhangban van az ENSZ klímacsúcsain tett vállalásokkal, ahol már 31 ország támogatja a nukleáris energia megháromszorozását a nettó zéró kibocsátási célok eléréséhez. Az amerikai kongresszus olyan törvényjavaslatokat készít elő, amelyek lehetővé tennék, hogy a multilaterális fejlesztési bankok – például a Világbank – is finanszírozhassanak nukleáris projekteket, megszüntetve ezzel a korábbi tiltásokat.
Közelgő nemzetközi nukleáris biztonsági gyakorlat
A Nemzetközi Atomenergia-ügynökség (IAEA) készül a ConvEx-3 vészhelyzeti gyakorlatára, amelyet 2025. június 24–25-én Romániában tartanak. A gyakorlat egy súlyos nukleáris vészhelyzetet szimulál a cernavodai atomerőműben, tesztelve a tagállamok és nemzetközi szervezetek felkészültségét és reagálóképességét. A ConvEx-3 a legmagasabb szintű IAEA vészhelyzeti gyakorlat, kulcsszerepet játszik a globális nukleáris biztonság és védelem erősítésében.
Politikai bizonytalanság Dél-Korea nukleáris terveiben
Dél-Korea 2025. június 3-i elnökválasztása hatással lehet az ország nukleáris reneszánszára. A vezető jelölt, Lee Jae-myung kijelentette, hogy „egyelőre” fenntartaná a nukleáris energiát, de hosszabb távon a megújulók felé mozdulna el. Ez bizonytalanságot okoz a koreai nukleáris ipar hazai és exportterveiben, ami kihatással lehet a globális ellátási láncokra és külföldi reaktorprojektekre is.
Iparági trendek és további fejlemények
- Japán új energiastratégiája maximalizálni kívánja a nukleáris energia részarányát, 2040-re mintegy 20%-ot célozva, különös hangsúlyt fektetve a következő generációs reaktorokra és a biztonság növelésére.
- Belgium kormánya és a francia Engie közműcég megállapodott a kulcsfontosságú reaktorok üzemidejének tízéves meghosszabbításáról, ami az európai nukleáris pálfordulás újabb jele.
- Az IAEA és a World Nuclear Association egyaránt növekvő nemzetközi érdeklődésről számol be az SMR-ek és fejlett reaktortechnológiák iránt, új projektek és partnerségek indulnak Ázsiában, Európában és Amerikában.
Források:
world-nuclear-news.org
nucnet.org
iaea.org
world-nuclear.org
govinfo.gov
whitehouse.gov -
 @ 5d4b6c8d:8a1c1ee3
2025-06-04 01:24:36
@ 5d4b6c8d:8a1c1ee3
2025-06-04 01:24:36Howdy stackers, this is the place to share your ~HealthAndFitness triumphs and challenges.
I was glad to hit my step goal today, since it's gloomy and rainy here. Once again, I ate too many cookies. Gotta stop being a cookie monster.
How'd you all do, today?
https://stacker.news/items/996659
-
 @ 21335073:a244b1ad
2025-05-21 16:58:36
@ 21335073:a244b1ad
2025-05-21 16:58:36The other day, I had the privilege of sitting down with one of my favorite living artists. Our conversation was so captivating that I felt compelled to share it. I’m leaving his name out for privacy.
Since our last meeting, I’d watched a documentary about his life, one he’d helped create. I told him how much I admired his openness in it. There’s something strange about knowing intimate details of someone’s life when they know so little about yours—it’s almost like I knew him too well for the kind of relationship we have.
He paused, then said quietly, with a shy grin, that watching the documentary made him realize how “odd and eccentric” he is. I laughed and told him he’s probably the sanest person I know. Because he’s lived fully, chasing love, passion, and purpose with hardly any regrets. He’s truly lived.
Today, I turn 44, and I’ll admit I’m a bit eccentric myself. I think I came into the world this way. I’ve made mistakes along the way, but I carry few regrets. Every misstep taught me something. And as I age, I’m not interested in blending in with the world—I’ll probably just lean further into my own brand of “weird.” I want to live life to the brim. The older I get, the more I see that the “normal” folks often seem less grounded than the eccentric artists who dare to live boldly. Life’s too short to just exist, actually live.
I’m not saying to be strange just for the sake of it. But I’ve seen what the crowd celebrates, and I’m not impressed. Forge your own path, even if it feels lonely or unpopular at times.
It’s easy to scroll through the news and feel discouraged. But actually, this is one of the most incredible times to be alive! I wake up every day grateful to be here, now. The future is bursting with possibility—I can feel it.
So, to my fellow weirdos on nostr: stay bold. Keep dreaming, keep pushing, no matter what’s trending. Stay wild enough to believe in a free internet for all. Freedom is radical—hold it tight. Live with the soul of an artist and the grit of a fighter. Thanks for inspiring me and so many others to keep hoping. Thank you all for making the last year of my life so special.
-
 @ 8bad92c3:ca714aa5
2025-06-03 18:02:33
@ 8bad92c3:ca714aa5
2025-06-03 18:02:33Marty's Bent

It's been a pretty historic week for the United States as it pertains to geopolitical relations in the Middle East. President Trump and many members of his administration, including AI and Crypto Czar David Sacks and Treasury Secretary Scott Bessent, traveled across the Middle East making deals with countries like Qatar, Saudi Arabia, the United Arab Emirates, Syria, and others. Many are speculating that Iran may be included in some behind the scenes deal as well. This trip to the Middle East makes sense considering the fact that China is also vying for favorable relationships with those countries. The Middle East is a power player in the world, and it seems pretty clear that Donald Trump is dead set on ensuring that they choose the United States over China as the world moves towards a more multi-polar reality.
Many are calling the events of this week the Riyadh Accords. There were many deals that were struck in relation to artificial intelligence, defense, energy and direct investments in the United States. A truly prolific power play and demonstration of deal-making ability of Donald Trump, if you ask me. Though I will admit some of the numbers that were thrown out by some of the countries were a bit egregious. We shall see how everything plays out in the coming years. It will be interesting to see how China reacts to this power move by the United States.
While all this was going on, there was something happening back in the United States that many people outside of fringe corners of FinTwit are not talking about, which is the fact that the 10-year and 30-year U.S. Treasury bond yields are back on the rise. Yesterday, they surpassed the levels of mid-April that caused a market panic and are hovering back around levels that have not been seen since right before Donald Trump's inauguration.


I imagine that there isn't as much of an uproar right now because I'm pretty confident the media freakouts we were experiencing in mid-April were driven by the fact that many large hedge funds found themselves off sides of large levered basis trades. I wouldn't be surprised if those funds have decreased their leverage in those trades and bond yields being back to mid-April levels is not affecting those funds as much as they were last month. But the point stands, the 10-year and 30-year yields are significantly elevated with the 30-year approaching 5%. Regardless of the deals that are currently being made in the Middle East, the Treasury has a big problem on its hands. It still has to roll over many trillions worth of debt over over the next few years and doing so at these rates is going to be massively detrimental to fiscal deficits over the next decade. The interest expense on the debt is set to explode in the coming years.
On that note, data from the first quarter of 2025 has been released by the government and despite all the posturing by the Trump administration around DOGE and how tariffs are going to be beneficial for the U.S. economy, deficits are continuing to explode while the interest expense on the debt has definitively surpassed our annual defense budget.
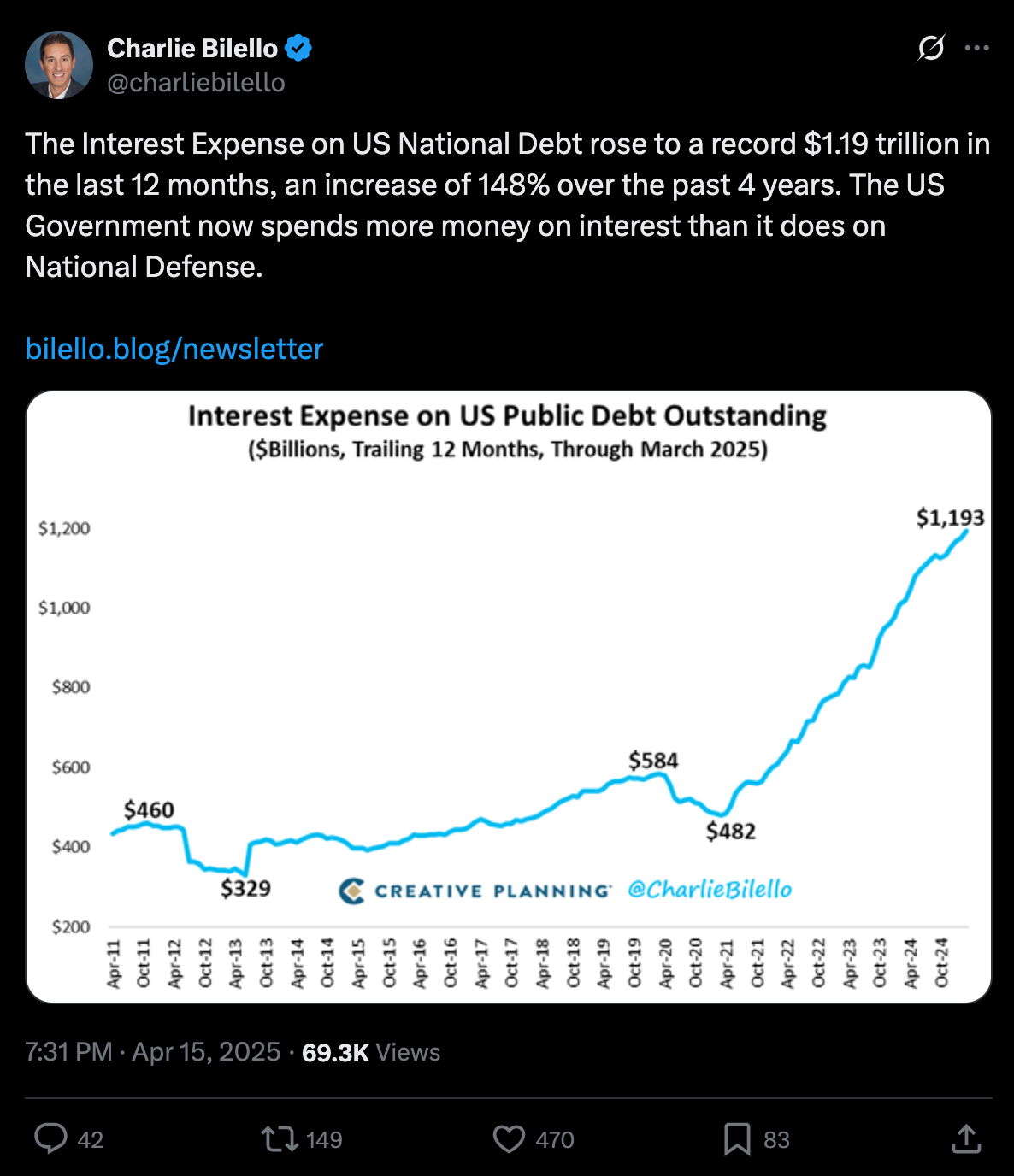
via Charlie Bilello
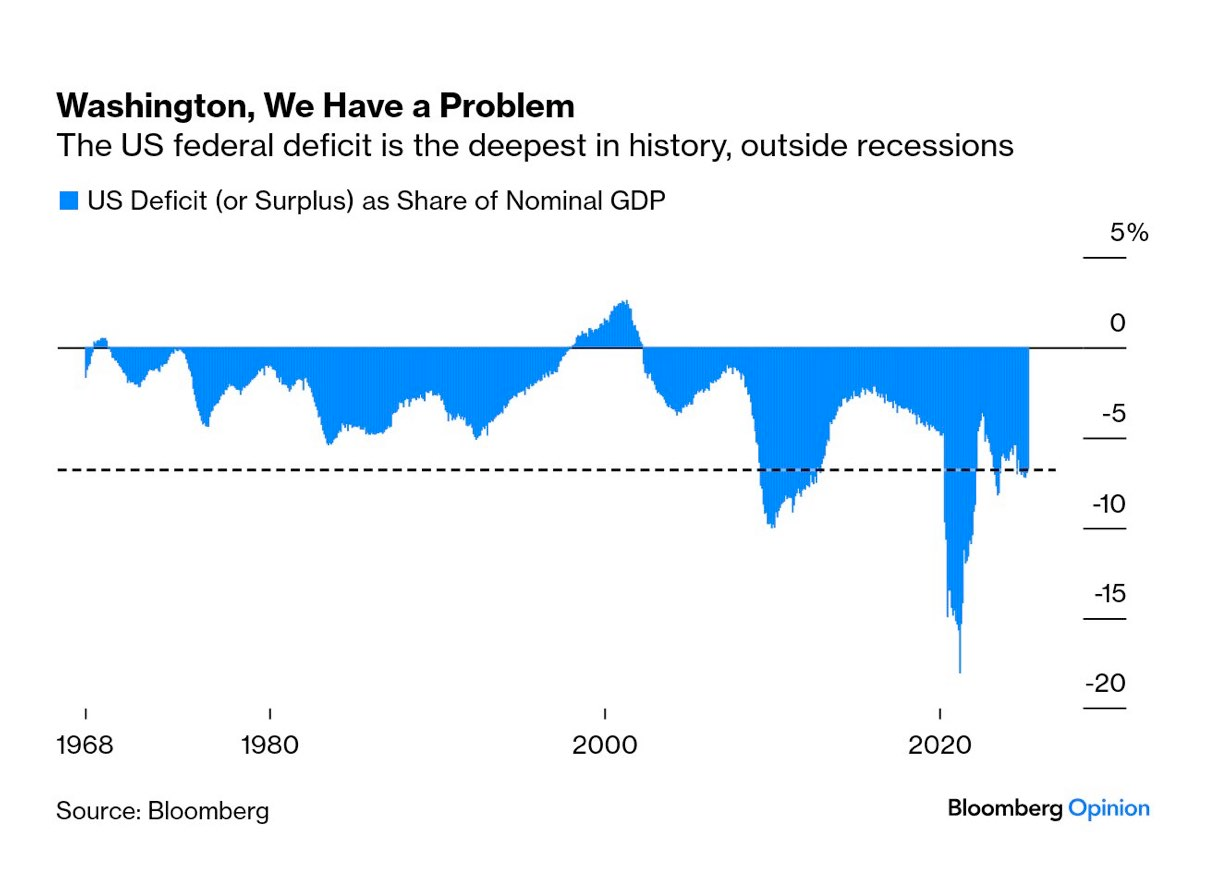
via Mohamed Al-Erian
To make matters worse, as things are deteriorating on the fiscal side of things, the U.S. consumer is getting crushed by credit. The 90-plus day delinquency rates for credit card and auto loans are screaming higher right now.

via TXMC
One has to wonder how long all this can continue without some sort of liquidity crunch. Even though equities markets have recovered from their post-Liberation Day month long bear market, I would not be surprised if what we're witnessing is a dead cat bounce that can only be continued if the money printers are turned back on. Something's got to give, both on the fiscal side and in the private markets where the Common Man is getting crushed because he's been forced to take on insane amounts of debt to stay afloat after years of elevated levels of inflation. Add on the fact that AI has reached a state of maturity that will enable companies to replace their current meat suit workers with an army of cheap, efficient and fast digital workers and it isn't hard to see that some sort of employment crisis could be on the horizon as well.
Now is not the time to get complacent. While I do believe that the deals that are currently being made in the Middle East are probably in the best interest of the United States as the world, again, moves toward a more multi-polar reality, we are facing problems that one cannot simply wish away. They will need to be confronted. And as we've seen throughout the 21st century, the problems are usually met head-on with a money printer.
I take no pleasure in saying this because it is a bit uncouth to be gleeful to benefit from the strife of others, but it is pretty clear to me that all signs are pointing to bitcoin benefiting massively from everything that is going on. The shift towards a more multi-polar world, the runaway debt situation here in the United States, the increasing deficits, the AI job replacements and the consumer credit crisis that is currently unfolding, All will need to be "solved" by turning on the money printers to levels they've never been pushed to before.
Weird times we're living in.
China's Manufacturing Dominance: Why It Matters for the U.S.
In my recent conversation with Lyn Alden, she highlighted how China has rapidly ascended the manufacturing value chain. As Lyn pointed out, China transformed from making "sneakers and plastic trinkets" to becoming the world's largest auto exporter in just four years. This dramatic shift represents more than economic success—it's a strategic power play. China now dominates solar panel production with greater market control than OPEC has over oil and maintains near-monopoly control of rare earth elements crucial for modern technology.
"China makes like 10 times more steel than the United States does... which is relevant in ship making. It's relevant in all sorts of stuff." - Lyn Alden
Perhaps most concerning, as Lyn emphasized, is China's financial leverage. They hold substantial U.S. assets that could be strategically sold to disrupt U.S. treasury market functioning. This combination of manufacturing dominance, resource control, and financial leverage gives China significant negotiating power in any trade disputes, making our attempts to reshoring manufacturing all the more challenging.
Check out the full podcast here for more on Triffin's dilemma, Bitcoin's role in monetary transition, and the energy requirements for rebuilding America's industrial base.
Headlines of the Day
Financial Times Under Fire Over MicroStrategy Bitcoin Coverage - via X
Trump in Qatar: Historic Boeing Deal Signed - via X
Get our new STACK SATS hat - via tftcmerch.io
Johnson Backs Stock Trading Ban; Passage Chances Slim - via X
Take the First Step Off the Exchange
Bitkey is an easy, secure way to move your Bitcoin into self-custody. With simple setup and built-in recovery, it’s the perfect starting point for getting your coins off centralized platforms and into cold storage—no complexity, no middlemen.
Take control. Start with Bitkey.
Use the promo code *“TFTC20”* during checkout for 20% off
Ten31, the largest bitcoin-focused investor, has deployed 158,469 sats | $150.00M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/invest.
Final thought...
Building things of value is satisfying.
Get this newsletter sent to your inbox daily: https://www.tftc.io/bitcoin-brief/
Subscribe to our YouTube channels and follow us on Nostr and X:
@media screen and (max-width: 480px) { .mobile-padding { padding: 10px 0 !important; } .social-container { width: 100% !important; max-width: 260px !important; } .social-icon { padding: 0 !important; } .social-icon img { height: 32px !important; width: 32px !important; } .icon-cell { padding: 0 4px !import
-
 @ e4950c93:1b99eccd
2025-06-05 10:23:39
@ e4950c93:1b99eccd
2025-06-05 10:23:39Marques
Nordkidz est une marque allemande qui crée à la demande des vêtements et linges pour les bébés, les enfants, et un peu pour leurs parents.
Matières naturelles utilisées dans les produits
⚠️ Attention, certains produits de cette marque contiennent des matières non naturelles, dont :
Catégories de produits proposés
Cette marque propose des produits intégralement en matière naturelle dans les catégories suivantes :
Vêtements
- Tailles vêtements : bébés, enfants, unisexe
- Hauts : pulls, t-shirts
- Bas : pantalons, pantalons de survêtement, shorts
- Tête et mains : bonnets, écharpes
Maison
- Linge : housses de pouf, langes, ponchos de bain
Autres informations
👉 En savoir plus sur le site de la marque
Où trouver leurs produits ?
- Nordkidz (en allemand, zone de livraison : Allemagne et Union Européenne) 💚 Via ce lien vous soutenez directement la marque.
📝 Tu peux contribuer à cette fiche en suggérant une modification en commentaire.
🗣️ Tu utilises des produits de cette marque ? Partage ton avis en commentaire.
⚡ Heureu-x-se de trouver cette information ? Soutiens le projet en faisant un don pour remercier les contribut-eur-ice-s.
-
 @ 51bbb15e:b77a2290
2025-05-21 00:24:36
@ 51bbb15e:b77a2290
2025-05-21 00:24:36Yeah, I’m sure everything in the file is legit. 👍 Let’s review the guard witness testimony…Oh wait, they weren’t at their posts despite 24/7 survellience instructions after another Epstein “suicide” attempt two weeks earlier. Well, at least the video of the suicide is in the file? Oh wait, a techical glitch. Damn those coincidences!
At this point, the Trump administration has zero credibility with me on anything related to the Epstein case and his clients. I still suspect the administration is using the Epstein files as leverage to keep a lot of RINOs in line, whereas they’d be sabotaging his agenda at every turn otherwise. However, I just don’t believe in ends-justify-the-means thinking. It’s led almost all of DC to toss out every bit of the values they might once have had.
-
 @ c9badfea:610f861a
2025-05-20 19:49:20
@ c9badfea:610f861a
2025-05-20 19:49:20- Install Sky Map (it's free and open source)
- Launch the app and tap Accept, then tap OK
- When asked to access the device's location, tap While Using The App
- Tap somewhere on the screen to activate the menu, then tap ⁝ and select Settings
- Disable Send Usage Statistics
- Return to the main screen and enjoy stargazing!
ℹ️ Use the 🔍 icon in the upper toolbar to search for a specific celestial body, or tap the 👁️ icon to activate night mode
-
 @ 42a071ab:3391e086
2025-06-05 20:06:56
@ 42a071ab:3391e086
2025-06-05 20:06:5688VIN đã từng bước khẳng định vị thế của mình trên thị trường bằng cách không ngừng đầu tư vào chất lượng dịch vụ và sự hài lòng của người dùng. Khác với những nền tảng thông thường, 88VIN chú trọng vào việc xây dựng một hệ sinh thái vận hành bài bản, nơi mọi quy trình đều được chuẩn hóa và tối ưu để đem lại hiệu suất cao nhất. Từ bước đăng ký tài khoản, xác thực thông tin, cho đến nạp – rút tiền và hỗ trợ khách hàng, tất cả đều được thiết kế một cách khoa học, rõ ràng và minh bạch. Sự tiện lợi trong thao tác và tính linh hoạt trong hệ thống đã giúp 88VIN tạo được sự tin tưởng vững chắc từ phía người dùng. Hệ thống hoạt động ổn định, tốc độ xử lý nhanh chóng, cùng đội ngũ chăm sóc khách hàng chuyên nghiệp, nhiệt tình 24/7 chính là những yếu tố làm nên thành công bền vững của 88VIN. Không chỉ vậy, nền tảng còn tích hợp công nghệ bảo mật hiện đại, bảo vệ an toàn tuyệt đối cho mọi thông tin và giao dịch cá nhân, giúp người dùng yên tâm tuyệt đối khi sử dụng.
Bên cạnh sự hoàn hảo về hệ thống, 88VIN còn gây ấn tượng bởi chính sách hỗ trợ người dùng rõ ràng, minh bạch và đầy tính nhân văn. Thay vì chỉ chú trọng vào mặt kỹ thuật, 88VIN hiểu rằng yếu tố con người mới là cốt lõi cho sự phát triển lâu dài. Chính vì vậy, đội ngũ chăm sóc khách hàng tại đây không chỉ được đào tạo bài bản mà còn luôn sẵn sàng lắng nghe, thấu hiểu và đồng hành cùng người dùng trong mọi tình huống. Mỗi phản hồi, dù là nhỏ nhất, đều được ghi nhận nghiêm túc để làm cơ sở nâng cấp chất lượng dịch vụ. Điều này giúp tạo nên một cộng đồng sử dụng 88VIN văn minh, gắn bó và ngày càng phát triển. Đồng thời, việc tối ưu hóa trải nghiệm người dùng được thể hiện qua từng chi tiết nhỏ, từ giao diện hiển thị, bố cục chức năng đến tốc độ phản hồi trên mọi thiết bị. Chính nhờ sự chăm chút tỉ mỉ đó, 88VIN không chỉ đáp ứng nhu cầu trước mắt mà còn luôn sẵn sàng cải tiến để bắt kịp xu hướng trong tương lai.
88VIN không đơn thuần là một nền tảng cung cấp dịch vụ chất lượng cao mà còn là biểu tượng của sự cam kết lâu dài đối với người dùng. Mỗi thành viên khi đến với 88VIN đều được đảm bảo quyền lợi rõ ràng, được đồng hành trong môi trường minh bạch và công bằng. Sự khác biệt của 88VIN chính là khả năng duy trì sự ổn định trong khi vẫn không ngừng đổi mới và hoàn thiện. Những giá trị mà 88VIN theo đuổi không chỉ nằm ở hiệu quả vận hành mà còn là sự tận tâm trong từng trải nghiệm của người dùng. Đây là yếu tố quyết định giúp nền tảng ngày càng chiếm được lòng tin và sự lựa chọn của cộng đồng. Trong thời đại mà sự cạnh tranh ngày càng khốc liệt, việc giữ vững đạo đức kinh doanh, coi trọng người dùng và luôn đặt chất lượng lên hàng đầu chính là con đường bền vững mà 88VIN đang theo đuổi. Nhờ vậy, 88VIN ngày càng khẳng định vị trí vững chắc, trở thành điểm đến tin cậy cho những ai tìm kiếm một nền tảng chuyên nghiệp, ổn định và thực sự vì lợi ích của người dùng.
-
 @ ac8bb9b0:70278acc
2025-06-05 18:12:29
@ ac8bb9b0:70278acc
2025-06-05 18:12:29Details
- ⏲️ Prep time: 15 min
- 🍳 Cook time: 20 min
- 🍽️ Servings: 12
Ingredients
- 1 and 1/2 cups (345g) mashed bananas (about 4 medium or 3 large ripe bananas)
- 1/3 cup (113g) honey
- 1 large egg
- 1/4 cup (56g) coconut oil, melted
- 1 teaspoon pure vanilla extract
- 1 cup (130g) whole wheat flour
- 1/2 cup (41g) natural unsweetened cocoa powder
- 1 teaspoon baking powder
- 1 teaspoon baking soda
- 1/2 teaspoon salt
- 1 cup (180g) semi-sweet or dark chocolate chips
Directions
- Preheat oven to 425°F (218°C). Spray a 12-count muffin pan with nonstick spray or line with cupcake liners. Set aside.
- In a medium bowl, mash the bananas up using a fork.* Try to mash up any large lumps. Once mashed, whisk in the honey, egg, coconut oil, and vanilla extract until combined. Set aside.
- In a large bowl, whisk the flour, cocoa powder, baking powder, baking soda, and salt together. Pour the wet ingredients into the dry ingredients and whisk until everything is combined. Fold in the chocolate chips, reserving some for the tops of the warm muffins.
- Spoon the batter evenly into each cup or liner, filling each all the way to the top.
- Bake for 5 minutes at 425°F (218°C); then, keeping the muffins in the oven, reduce heat to 350°F (177°C) and continue baking for another 15–17 minutes or until a toothpick inserted in the center comes out clean. The total time these muffins take in the oven is about 20–21 minutes, give or take. (For mini muffins, bake 11–13 minutes at 350°F (177°C) the whole time.)
- Press any remaining chocolate chips into the tops of the warm muffins. Allow the muffins to cool for 5 minutes in the muffin pan, and then transfer to a wire rack to continue cooling, or enjoy warm.
- Muffins stay fresh covered at room temperature for a few days, then transfer to the refrigerator for up to 1 week.
-
 @ 58537364:705b4b85
2025-06-03 15:22:59
@ 58537364:705b4b85
2025-06-03 15:22:59…. “คนเรา โดยเฉพาะสมัยนี้ พูดกันอีกที่หนึ่งก็พูดได้ว่า ถูกสร้างขึ้นมาด้วยหนังสือ, หนังสือมันสร้างคนขึ้นมา คือว่า..อ่านหนังสืออะไรมาก อ่านหนังสืออะไรมาก หนังสือนั้นก็สร้างคนคนนั้นขึ้นมา, สร้างจิตใจของคนนั้นขึ้นมา โดยไม่รู้สึก
…. ไปดูหนังสือที่เขาอ่าน อ่านมากที่สุด เราก็รู้ได้ว่า..คนนี้มีจิตใจเป็นอย่างไร. หนังสือที่นิยมสั่งกันมามาก ล้วนแต่เป็นหนังสือที่ยั่วยวนทางวัตถุ หรือลุ่มหลงทางวัตถุ : แล้วอย่างดีที่สุดก็เอามาให้เสียเวลา อ่านให้มันมึนหัวเล่น อย่างนั้นแหละ จนไม่มีเวลาที่จะไปอ่านหนังสือธรรมะที่แท้จริง เพราะว่ามีหนังสืออื่นมาก วางอยู่มาก ยั่วยวนให้อ่านมากกว่า
…. แม้แต่พระเณร ก็เป็นอย่างนี้ อ่านหนังสือพิมพ์, หรืออ่านหนังสือภาษา, เรียนภาษาต่างประเทศ หรือว่าเรียนวิชานั่น นี่ ล้วนแต่เป็นเรื่องวัตถุ เรื่องอาชีพ เรื่องความดีความเด่น ที่ฝันไว้ในจิตในใจ, ด้วยความหวังความทะเยอทะยานทั้งนั้น แล้วจะเอากําลังใจ หรือมันสมอง หรืออะไรที่ไหนมาเข้าใจ ธรรมะ ธัมโม ได้
…. ทีนี้ ยิ่งนอกวัดออกไป ก็ยิ่งไกลไปใหญ่ : หอสมุดของมหาวิทยาลัย, หอสมุดของชาติ ของอะไร ก็ล้วนแต่เป็น “หอสมุดของซาตาน” มากยิ่งขึ้นเท่านั้น เพราะไปมีมันขึ้น หรือสร้างมันไว้ ด้วยความอยากดีอยากเด่น ด้วยความอยากที่จะร่ำรวยวัตถุทั้งนั้น ฉะนั้น จึงมีผลทําให้คนทั้งโลกนี้เป็นทาสของวัตถุ พร้อมที่จะสร้างวิกฤตการณ์ ขึ้นในโลกในอนาคต
…. แล้วรองลงมาจากนั้น ก็คือ มันมากจนทําให้เวียนหัว เป็น..“บ้าหอบฟาง”; อย่างที่ว่าแล้วว่าเล่า ว่าเป็นบ้าหอบฟาง, รู้อะไรท่วมหัวก็เอาตัวไม่รอด, เรียนจบมหาวิทยาลัยแล้ว ก็ยังไม่รู้ว่าเกิดมาทําไม ?, เรียนมหาวิทยาลัยจบแล้ว อ่านหนังสือในห้องสมุดของมหาวิทยาลัยจบแล้ว ก็ยังเป็นเด็กอมมือ ไม่รู้ว่า.. “กูนี่ เกิดมาทําไม ?”. ดูซิ!, แล้วจะเรียกว่า “อุดมศึกษา” ได้อย่างไรกัน ? แม้แต่เกิดมาทําไม? ก็ยังไม่รู้ นี่การศึกษาสมัยนี้ หอสมุดหรือห้องสมุดของสมัยนี้ มันเป็นอย่างนี้
…. ทีนี้ เมื่อไม่รู้ว่าเกิดมาทําไม ? มันก็ไม่มีอะไร นอกจากเป็นทาสของวัตถุ ที่หวังว่าจะสนุกสนาน เอร็ดอร่อย มีเกียรติ มีอํานาจวาสนา มีอะไรไปทํานองนั้น นี่แหละ คือการตกเป็นทาสของวัตถุ การตกเป็นทาสของอายตนะ คือ ตา หู จมูก ลิ้น กาย ใจ การเล่าเรียนศึกษาขวนขวายนั้น เพื่อจะเป็นทาส ของ ตา หู จมูก ลิ้น กาย ใจ ในการที่จะแสวงหาความสนุกสนาน เอร็ดอร่อย ทางเนื้อทางหนัง มีเท่านี้ การศึกษาและห้องสมุด” . พุทธทาสภิกขุ ที่มา : ธรรมบรรยายชุดชุมนุมล้ออายุ หัวข้อเรื่อง “ยิ่งจะทำให้ดี โลกมันยิ่งบ้า” บรรยาย ณ ลานหินโค้ง กัณฑ์ค่ำ เมื่อวันที่ ๒๗ พฤษภาคม ๒๕๑๓ จากหนังสือชุดธรรมโฆษณ์ เล่มชื่อว่า “ชุมนุมล้ออายุ เล่ม ๑” หน้า ๕๑๒-๕๑๓
-
 @ 2cde0e02:180a96b9
2025-06-05 21:45:00
@ 2cde0e02:180a96b9
2025-06-05 21:45:00日本の姫
https://stacker.news/items/998335
-
 @ cae03c48:2a7d6671
2025-06-03 12:01:09
@ cae03c48:2a7d6671
2025-06-03 12:01:09Bitcoin Magazine

Sberbank, Russia’s Biggest Bank, Launches Structured Bond Tied to BitcoinSberbank, the largest bank in Russia, has launched a new structured bond that ties investor returns to the performance of Bitcoin and the U.S. dollar-to-ruble exchange rate. This new financial product represents one of the first moves by a major Russian institution to offer Bitcoin-linked investments under recently updated national regulations.
BREAKING:
 Russia's largest bank Sberbank launches structured bonds linked to Bitcoin. pic.twitter.com/LtD26jPS0x
Russia's largest bank Sberbank launches structured bonds linked to Bitcoin. pic.twitter.com/LtD26jPS0x— Bitcoin Magazine (@BitcoinMagazine) June 2, 2025
The structured bond is initially available over the counter to a limited group of qualified investors. According to the announcement, it allows investors to earn based on two factors: the price performance of BTC in U.S. dollars and any strengthening of the dollar compared to the Russian ruble.
Unlike typical Bitcoin investments, this product does not require the use of a Bitcoin wallet or foreign platforms. “All transactions [are] processed in rubles within Russia’s legal and infrastructure systems,” Sberbank stated, highlighting compliance with domestic financial protocols.
In addition to the bond, Sberbank has announced plans to launch similar structured investment products with Bitcoin exposure on the Moscow Exchange. The bank also revealed it will introduce a Bitcoin futures product via its SberInvestments platform on June 4, aligning with the product’s debut on the Moscow Exchange.
These developments follow a recent policy change by the Bank of Russia, which now permits financial institutions to offer Bitcoin-linked instruments to qualified investors. This shift opens the door for Bitcoin within the country’s traditional financial markets.
While Russia has previously taken a cautious approach to digital assets, Sberbank’s launch of a Bitcoin-linked bond and upcoming futures product marks a new phase of adoption—one that blends Bitcoin exposure with existing financial infrastructure.
The bank’s structured bond may signal a growing interest in regulated access to Bitcoin, especially within large financial institutions.
This post Sberbank, Russia’s Biggest Bank, Launches Structured Bond Tied to Bitcoin first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ 05a0f81e:fc032124
2025-06-05 18:36:08
@ 05a0f81e:fc032124
2025-06-05 18:36:08Akhenaten (originally named Amenhotep IV) was a pharaoh of ancient Egypt known for radically transforming Egyptian religion, art, and culture. He is most famous for promoting the worship of one god—Aten, the sun disk—marking one of the earliest recorded movements toward monotheism.
Early Life and Rise to Power of pharaoh Akhenaten.
The Birth Name was Amenhotep IV, and he was born Around 1380 BCE. By Pharaoh Amenhotep III, and the mother Likely Queen Tiye. He grew up and married a Wife, Nefertiti, one of Egypt's most iconic queens. He have children, Including daughters and likely the father of Tutankhamun (King Tut).
Amenhotep IV ascended the throne around 1353 BCE, succeeding his father, a powerful and prosperous pharaoh, and there was a Religious Revolution.
A Shift Toward Monotheism
Around his 5th regnal year, Amenhotep IV changed his name to Akhenaten, meaning "Effective for Aten".
He abandoned the traditional Egyptian pantheon, especially the powerful god Amun, and elevated Aten as the sole god.
This was a dramatic break from Egypt's deeply rooted polytheistic religion.
The capital city Akhetaten (Modern-day Amarna). Akhenaten moved the capital from Thebes to a new city he built from scratch: Akhetaten (Horizon of Aten).
The city was dedicated entirely to the Aten religion and became a center of art, culture, and politics.
Nefertiti was not just a queen but a powerful co-ruler. Some theories suggest she may have ruled independently for a time after Akhenaten’s death (possibly as Neferneferuaten).
They had at least six daughters. The identity of Akhenaten's sons is debated, but Tutankhamun is widely believed to be his son, possibly by a secondary wife.
Decline and Death
Akhenaten died around 1336 BCE after a 17-year reign.
After his death, his successors (including Tutankhamun) restored traditional religion, abandoned Atenism, and moved the capital back to Thebes.
His monuments were defaced, and his name was erased from king lists, a process known as damnatio memoriae (damnation of memory).
Legacy
Akhenaten is remembered as:
A visionary who introduced monotheism before it appeared in other cultures.
A heretic who defied over a thousand years of religious tradition.
A reformer whose bold changes caused cultural upheaval.
His religious revolution was short-lived, but modern historians and archaeologists regard him as one of the most fascinating and controversial figures in ancient history.
The reasons why Pharaoh Akhenaten introduced monotheism, the worship of Aten, the sun disk, as the one true god are still debated by historians, but several key political, religious, personal, and philosophical factors likely contributed.
✅ Main Reasons Why Akhenaten Introduced Monotheism
- Religious Reform: Belief in a Universal Power
Akhenaten may have genuinely believed in Aten as the supreme creator and life-giver.
The sun was already important in Egyptian religion (Ra, Amun-Ra), but Akhenaten stripped away all personification, choosing the sun's disk (Aten) as a pure, abstract symbol of divine power.
He saw Aten as omnipresent, providing light and life to everything and everyone equally.
- Political Motivation: Weaken the Power of the Priests
The priesthood of Amun at Thebes had become extremely wealthy and powerful, almost a state within a state. By elevating Aten and banning Amun's worship, Akhenaten dismantled the influence of the Amun priests and centralized religious power in his own hands. He made himself the sole mediator between Aten and the people, increasing royal control.
- Personal Vision and Identity
Akhenaten may have had a personal religious experience or conviction that shaped his devotion to Aten.
His new name, “Akhenaten,” meaning “Effective for the Aten,” reflects a deep, personal connection to this god.
He often depicted himself and his family in direct contact with Aten, showing a highly intimate and unique belief system.
- Philosophical and Artistic Shift
Akhenaten's reign saw a revolution in art, emphasizing naturalism, emotion, and individuality.
This change in thinking may reflect a broader philosophical shift toward a more abstract and spiritual understanding of the divine unified in Aten.
Atenism removed the idea of gods with human forms, replacing them with a universal force (the sun's light).
- Reaction Against Religious Corruption or Complexity
Traditional Egyptian religion had hundreds of gods, rituals, and temple hierarchies.
Akhenaten may have seen the system as corrupt, ritualistic, and too complex for ordinary people.
Atenism was simple, focused, and accessible, with the sun’s light reaching everyone equally.
- Political Instability or Health Issues (Speculative)
Some theories suggest Akhenaten’s appearance (depicted with elongated head, wide hips, etc.) may reflect a genetic disorder (e.g., Marfan syndrome or Froehlich's syndrome).
If he was sickly, he may have been drawn to religious introspection or spiritual reform.
Others suggest that political instability or unrest during his early reign may have motivated a bold unifying reform.
Summary
Akhenaten’s monotheism was unprecedented in Egypt’s long religious history. Whether he was a spiritual visionary, a political tactician, or both, his religious revolution stands out as one of the most dramatic and controversial in ancient history.
-
 @ b1ddb4d7:471244e7
2025-06-05 09:01:10
@ b1ddb4d7:471244e7
2025-06-05 09:01:10Starting January 1, 2026, the United Kingdom will impose some of the world’s most stringent reporting requirements on cryptocurrency firms.
All platforms operating in or serving UK customers-domestic and foreign alike-must collect and disclose extensive personal and transactional data for every user, including individuals, companies, trusts, and charities.
This regulatory drive marks the UK’s formal adoption of the OECD’s Crypto-Asset Reporting Framework (CARF), a global initiative designed to bring crypto oversight in line with traditional banking and to curb tax evasion in the rapidly expanding digital asset sector.
What Will Be Reported?
Crypto firms must gather and submit the following for each transaction:
- User’s full legal name, home address, and taxpayer identification number
- Detailed data on every trade or transfer: type of cryptocurrency, amount, and nature of the transaction
- Identifying information for corporate, trust, and charitable clients
The obligation extends to all digital asset activities, including crypto-to-crypto and crypto-to-fiat trades, and applies to both UK residents and non-residents using UK-based platforms. The first annual reports covering 2026 activity are due by May 31, 2027.
Enforcement and Penalties
Non-compliance will carry stiff financial penalties, with fines of up to £300 per user account for inaccurate or missing data-a potentially enormous liability for large exchanges. The UK government has urged crypto firms to begin collecting this information immediately to ensure operational readiness.
Regulatory Context and Market Impact
This move is part of a broader UK strategy to position itself as a global fintech hub while clamping down on fraud and illicit finance. UK Chancellor Rachel Reeves has championed these measures, stating, “Britain is open for business – but closed to fraud, abuse, and instability”. The regulatory expansion comes amid a surge in crypto adoption: the UK’s Financial Conduct Authority reported that 12% of UK adults owned crypto in 2024, up from just 4% in 2021.
Enormous Risks for Consumers: Lessons from the Coinbase Data Breach
While the new framework aims to enhance transparency and protect consumers, it also dramatically increases the volume of sensitive personal data held by crypto firms-raising the stakes for cybersecurity.
The risks are underscored by the recent high-profile breach at Coinbase, one of the world’s largest exchanges.
In May 2025, Coinbase disclosed that cybercriminals, aided by bribed offshore contractors, accessed and exfiltrated customer data including names, addresses, government IDs, and partial bank details.
The attackers then used this information for sophisticated phishing campaigns, successfully deceiving some customers into surrendering account credentials and funds.
“While private encryption keys remained secure, sufficient customer information was exposed to enable sophisticated phishing attacks by criminals posing as Coinbase personnel.”
Coinbase now faces up to $400 million in compensation costs and has pledged to reimburse affected users, but the incident highlights the systemic vulnerability created when large troves of personal data are centralized-even if passwords and private keys are not directly compromised. The breach also triggered a notable drop in Coinbase’s share price and prompted a $20 million bounty for information leading to the attackers’ capture.
The Bottom Line
The UK’s forthcoming crypto reporting regime represents a landmark in financial regulation, promising greater transparency and tax compliance. However, as the Coinbase episode demonstrates, the aggregation of sensitive user data at scale poses a significant cybersecurity risk.
As regulators push for more oversight, the challenge will be ensuring that consumer protection does not become a double-edged sword-exposing users to new threats even as it seeks to shield them from old ones.
-
 @ c4f5e7a7:8856cac7
2025-06-03 08:15:33
@ c4f5e7a7:8856cac7
2025-06-03 08:15:33I've managed to amass three SN profiles.
Is there a way to combined these?
@k00b @ek
https://stacker.news/items/995836
-
 @ cae03c48:2a7d6671
2025-06-05 21:01:38
@ cae03c48:2a7d6671
2025-06-05 21:01:38Bitcoin Magazine

Moscow Exchange Launches Bitcoin Futures For Qualified InvestorsThe Moscow Exchange, Russia’s largest exchange group, announced the launch of Bitcoin futures contracts on June 4th, 2025. The new derivatives will allow qualified investors in Russia to gain exposure to bitcoin prices without directly owning it.
The bitcoin futures contracts are cash-settled in Russian rubles and will be tied to the iShares Bitcoin Trust ETF (IBIT) that trades on U.S. exchanges. The IBIT ETF tracks the price of bitcoin, with each share representing 0.00068 bitcoin.
BREAKING:
 Russia’s largest exchange, Moscow Exchange launches #Bitcoin futures trading for qualified investors. pic.twitter.com/J9htJUWpLw
Russia’s largest exchange, Moscow Exchange launches #Bitcoin futures trading for qualified investors. pic.twitter.com/J9htJUWpLw— Bitcoin Magazine (@BitcoinMagazine) June 4, 2025
Trading for the new bitcoin futures kicked off on Wednesday, with the first contracts expiring in September 2025. Each futures contract will be denominated in U.S. dollars per bitcoin but settled in rubles.
The launch of bitcoin futures on the Moscow Exchange comes after increased interest in Bitcoin exposure from Russian financial institutions. In May, Russia’s central bank formally permitted the offering of crypto-linked securities and derivatives to qualified investors. Prior to this, direct investment in Bitcoin was discouraged.
Sberbank, Russia’s largest bank, also announced plans to unveil its own bitcoin futures product in addition to the Moscow Exchange’s offering. The bank is launching exchange-traded notes that track Bitcoin’s price without direct ownership.
Bitcoin futures and other crypto-derivatives have seen surging interest recently as the Bitcoin and crypto industry matures. The move comes as an increasing number of countries have started adding Bitcoin to their reserves.
As Bitcoin adoption increases, investors and financial institutions are seeking more routes to gain exposure to Bitcoin. The launch of futures on the Moscow Exchange provides regulated bitcoin exposure to qualified Russian investors. But direct ownership of “physical” bitcoin remains off limits for most in Russia’s traditional finance sector.
This post Moscow Exchange Launches Bitcoin Futures For Qualified Investors first appeared on Bitcoin Magazine and is written by Vivek Sen.
-
 @ 04c915da:3dfbecc9
2025-05-20 15:53:48
@ 04c915da:3dfbecc9
2025-05-20 15:53:48This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ 527337d5:93e9525e
2025-06-05 03:09:02
@ 527337d5:93e9525e
2025-06-05 03:09:02The Algorithmic Pursuit of Connection: A Five-Book Journey into the Self
As a researcher, hitting my thirties and the winding down of a significant project prompted a crucial re-evaluation of life's latter half. While I'd successfully applied probabilistic control theory to one-on-one interactions, the complexities of group dynamics remained a persistent challenge. My recent dive into five diverse books on human relationships inadvertently became a profound journey of self-discovery, fundamentally reshaping my perspective on social connections.
Neil Strauss: A Mirror Reflecting the Self's Evolution
Neil Strauss's The Truth resonated deepest among my recent reads. The author's battle with sex addiction uncomfortably mirrored my own past struggles: the fragile self-esteem stemming from rejection, the hubris born of early successes, and the tendency to view women as mere objects of manipulation. It felt eerily prescient, a glimpse into a potential future.
Yet, I found myself arriving at Strauss's ultimate conclusion – the paramount importance of self-preparation and community – far sooner than he did. This acceleration wasn't accidental; it was the result of intense focus on individual experiences, meticulously replayed and analyzed in my mind. The book, therefore, served less as a revelation and more as a powerful validation of my own journey of introspection and root-cause analysis.
Quantifying Connection: The Promise and Limits of Mathematical Models
Hannah Fry's The Mathematics of Love offered a kindred spirit in its attempt to quantify human relationships. While I appreciate the mathematical lens, Fry's models primarily concern dyadic relationships (N=2), relying on relatively simple systems of two-variable ordinary differential equations. For me, these are akin to linear models, sufficient only up to a certain point. Beyond N=4, the dependencies become exponentially complex.
My own pursuit extends to understanding and optimizing group dynamics within complex systems. This involves multi-variable problems (N $\ge$ 3) and the application of network theory, a far more sophisticated approach. Human collectives, after all, are systems of nodes and edges, where information propagates in predictable ways. My focus is on deriving optimal behavioral controls within these intricate frameworks.
Conversely, Men Are from Mars, Women Are from Venus initially struck me as bordering on conspiracy theory. However, its latter half proved unexpectedly useful. Its clear enumeration of male and female desires, and its articulation of common points of conflict, presented a practical template for communication styles. In a systemic view, this serves as a rudimentary, yet functional, interface design for complex social interactions.
A Dispassionate Critique of Relationship Dogma
My drive for efficiency and systematic understanding led to a rather blunt assessment of certain relationship classics. The New Science of Adult Attachment felt disorganized and frustratingly anecdotal. Lacking a coherent theoretical framework, it burdened the reader with deciphering meaning from a jumble of examples. Its inefficiency was, frankly, its most irksome flaw.
Similarly, Dale Carnegie's How to Win Friends and Influence People struck me as closer to pseudoscience than social science. Its plethora of specific anecdotes obscured any underlying principle. Given my deep engagement with social engineering – a discipline that systematically and practically analyzes human interaction – Carnegie's work appeared largely irrelevant and inefficient. From my perspective, which views humans as objective systems to be analyzed with mathematical rigor, such unstructured approaches hold little value.
The Unveiling of a Core Principle: Humans as Systems
This intensive reading period solidified my most crucial insight: humans, at their core, are systems. This understanding allows for a dispassionate, methodical approach to human collectives, mitigating unnecessary emotional friction.
This revelation has sharply refined my future learning trajectory. I'm now prioritizing foundational theories like graph theory and network theory over anecdotal accounts of human behavior. By mastering these theoretical underpinnings, I aim to precisely model complex human interactions as systems of nodes and edges, enabling the derivation of optimal behavioral controls within communities.
My choice of the term "target for capture" for individuals stems from a personal aversion to perceived equality in certain human interactions, a mechanism to avoid cognitive dissonance. This rational approach, I believe, is key to cultivating secure attachment styles – relationships demonstrably sustainable in the long term. My philosophy is to strategically approach the initial engagement, then transition to a stable, enduring connection. It's a calculated, dispassionate method for achieving desired relational outcomes.
Ultimately, this period of reading wasn't just about acquiring knowledge; it was a profound journey of self-discovery, clarifying my personal frameworks for navigating life's complexities and forging meaningful, yet strategically managed, connections.
-
 @ 04c915da:3dfbecc9
2025-05-20 15:50:22
@ 04c915da:3dfbecc9
2025-05-20 15:50:22There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ 20e7c953:3b8bcb21
2025-06-05 10:32:40
@ 20e7c953:3b8bcb21
2025-06-05 10:32:4021… That number means something. A reminder that limits create value - both in Bitcoin and in life.
Every June 21st, skaters around the world remind us that freedom is something you make yourself - one push at a time only constrained by your own limitations.
This year in Vientiane, we’re proud to support one of the few real skate spots in Laos. A place built and held together by skaters for skaters.
Expect around 50 locals - from young kids to older heads - showing up not just to skate, but to hold space for each other. No ego, no filters, just boards, fun and respect.
Bircoiners have lots to learn from these communities on this regard. Go skate and you'll find out.
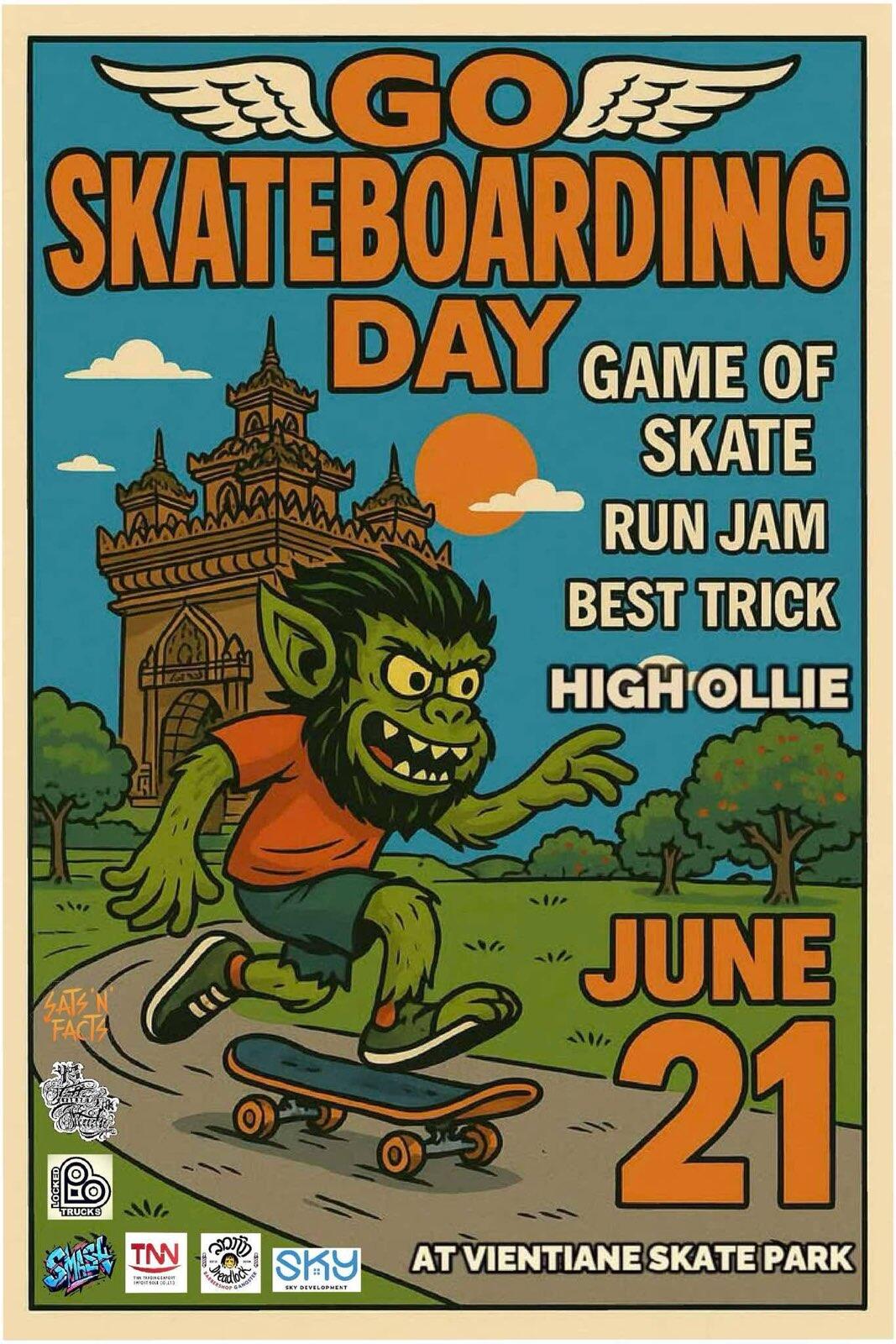
SnF
Laostr
Skateboardingisfun
Skate4Fun
-
 @ 04c915da:3dfbecc9
2025-05-20 15:47:16
@ 04c915da:3dfbecc9
2025-05-20 15:47:16Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 2f5de000:2f9bcef1
2025-06-05 17:33:37
@ 2f5de000:2f9bcef1
2025-06-05 17:33:37I've wanted to write this piece for months. Not because I have anything against Jack Mallers personally - quite the opposite. But because I've watched a pattern emerge in Bitcoin that mirrors one of the most chilling dynamics in Atlas Shrugged: the systematic destruction of our most productive builders by the very people who should be celebrating them.
We are the looters. And Jack might just be our Hank Rearden.
The Underdog's Dilemma
There's a cruel irony in how we treat success in Bitcoin. We champion the underdog, root for the builder in the garage, celebrate the cypherpunk taking on the establishment. But the moment that underdog succeeds - the moment they scale, grow, and inevitably have to navigate the messy realities of the existing system - we turn on them with the ferocity of the same establishment we claim to oppose.\ \ Jack began building Zap (which evolved into Strike) from his parents home in Chicago. Strike has grown into one of the most seamless fiat-to-bitcoin on-ramps for everyday users. No complexity, just pure utility. From day one, he's operated at a level of transparency that would make most CEO's uncomfortable. He's been building in public, taking feedback, admitting mistakes, and iterating - sometimes within hours of criticism.
The Rearden Parallel
In Atlas Shrugged, Hank Rearden creates Rearden Metal - a revolutionary alloy that's stronger, lighter, and more efficient than anything that came before. Instead of celebration, he faces endless scrutiny, regulation, and demands to prove is worthiness. The people who benefit from his innovation spend their time questioning his motives, dissecting his business practices, and demanding he justify his success.
Sound familiar?
Jack comes from a finance background - his father and grandfather were in the industry. This isn't a liability; it's an asset. He understands the beast we're fighting. He's been a Bitcoiner since 2013 with a spotless track record in a space littered with exit scams and broken promises. His values align with proof of work, individualism, and the radical idea that bitcoin is for everyone.
Yet when he helps launch 21 Capital, we don't see innovation - we see betrayal. When he navigates regulatory requirements to build products that can actually reach mainstream adoption, we don't see pragmatism - we see capitulation.
The Scarred Perspective
Our skepticism isn't entirely unfounded. We've been burned before. Mt. Gox, FTX, Three Arrows Capital, Celcius, Terra/ LUNA, BlockFi, Bitconnect, Voyager, QuadrigaCX - the graveyard of Bitcoin is littered with the corpses of trusted institutions. We've learned, painfully, that trust must be earned and verified.
But somewhere along the way, our healthy skepticism has metastasized into destructive paranoia. We've become so focused on protecting ourselves from the next SBF that we're attacking the people building the future we claim to want.
I'm guilty of this myself. I've made scathing attacks on my Nostr feed, comparing Jack to SBF, scrutinising contract clauses about re-hypothecation, and questioning his every move privately. I was viewing his actions through the lens of collective trauma rather than the reality of his long track record.
The Looters Paradox
Here's the uncomfortable truth: we're not just passive observers in this drama. We're active participants. We're the looters.
In Atlas Shrugged, the looters don't necessarily steal directly. They steal time, energy, and focus. They create bureaucracy, demnd endless justification, and burden the productive with the weight of constant explanation. They don't build competing products - they just tear down what others have built.
Everytime we demand Jack explain his business model for the hundredth time, we're stealing his time. Every time we scrutinize his partnerships without offering alternatives, we're creating bureaucracy . Everytime we attack his character rather than his arguments, we're furthering the system we claim to oppose.
The free market will create products whether we like them or not. People will build services that use bitcoin as collateral, create lending products, and navigate regulatory frameworks. The question isn't whether these products will exist - it's whether they'll be built by people who share our values or by those who don't.
The Atlantis Risk
The producers eventually withdraw from society in Atlas Shrugged, retreating to Galt's Gulch (Atlantis) and leaving the looters to face the consequences of their destructive behaviour. The economy collapses because the people who actually build things decided it wasn't worth the hassle anymore.
We're walking dangerously close to this precipice in Bitcoin. We're creating an environment where our most capable builders might just decide it's not worth it. Where the hassle of dealing with our constant scrutiny and bad-faith attacks outweighs the mission of building the future.
Jack has been more patient with our criticism than we deserve. He's addressed concerns publicly, changed the course when necessary, and continued building despite the noise. But patience has limits. At some point, even the most mission-driven builders will ask themselves: "Why am I doing this?"
The Path Forward
I don't know enough about finance to fully understand everything Jack is building with 21 Capital. Neither do most of his critics. But I know enough about Bitcoin to recognise someone who's been fighting the good fight for over a decade.
This doesn't mean we should trust blindly. It doesn't mean we should stop asking questions or demanding transparency. But it does mean we should approach our builders with the same benefit of the doubt we'd want for ourselves.
We need to distinguish between healthy skepticism and destructive paranoia. Between holding people accountable and tearing them down. Between being vigilant and being looters.
The fiat system is the real enemy here. It's massive, entrenched, and infinitely resourcesful. It will adapt, co-opt, and corrupt everything it touches. Fighting it requires builders who are willing to get their hands dirty, navigate imperfect systems, and make pragmatic compromises while holding onto their core values.
We can continue to be looters, tearing down what we don't understand and driving our best builders toward their own version of Atlantis. Or we can be what we claim to be: supporters of the free market, believers of proof of work, and champions of those building the future.
Don't trust. Verify. But remember: verification works both ways.
-
 @ e8646d56:72dab368
2025-06-03 08:15:30
@ e8646d56:72dab368
2025-06-03 08:15:30eee
-
 @ a296b972:e5a7a2e8
2025-06-04 22:06:06
@ a296b972:e5a7a2e8
2025-06-04 22:06:06In dem Video geht es um Dietrich Bonhoeffer, wie er sich zu Dummheit und vorsätzlicher bzw. rationaler Ignoranz geäußert hat. Schon seit einiger Zeit geht bei vielen Seltsames vor: Sie werden mit einem Thema persönlich konfrontiert und postum gibt es genau zu diesem Thema ein Video oder einen Artikel. Das kommt manchmal so vor, wie ein Frage- und Antwort-Spiel innerhalb der Schwarm-Intelligenz. Irgendwie spooky.
Die erschreckende Theorie der Dummheit, die Sie nie hören sollten - Dietrich Bonhoeffer: https://www.youtube.com/watch?v=PH-Vs5ILEko
Dem Entdecken, oder besser, dem Auf-einen-Zukommen, ist dieser E-Mail-Schriftverkehr in zeitlichem Zusammenhang vorausgegangen:
Nachfrage zu einem Aufruf durch einen Mitarbeiter zur Blutspende in einem Unternehmen mit über 100 Mitarbeitern über den E-Mail-Verteiler:
Lieber XXXXXXX,
danke zunächst für Dein Engagement.
In meiner näheren Familie gibt es jemanden, der regelmäßig Blut spendet, daher bin ich ein wenig für das Thema sensibilisiert.
Seit Du die E-Mail verschickt hast, gehe ich damit „schwanger“, ob ich ein vielleicht „heißes Eisen“ anfassen soll.
In den angehängten Informationen (des Roten Kreuzes) steht, dass das gespendete Blut auf bestimmte „Verunreinigungen“ durch Vorerkrankungen untersucht wird. Was nicht aufgeführt ist, ist eine Untersuchung, von der ich noch nicht einmal weiß, ob sie überhaupt schon durchgeführt wurde, und wenn ja, zu welchem Ergebnis sie gekommen ist, ob das gespendete Blut auch mit Substanzen der Corona-Gen-Behandlung verunreinigt sein kann. Leider zeigen ja die aktuellen Erkenntnisse, dass das Spike-Protein noch nach Jahren aktiv sein kann. Auch in gespendetem Blut? Die konkrete Frage wäre, ob das Rote Kreuz definitiv ausschließen kann, dass das nicht der Fall ist, damit ein möglicher Schaden nicht die Gefahr läuft, größer zu sein, als der Nutzen.
Soweit ich weiß, hat das Rote Kreuz bis heute keine separaten Blutbanken von „geimpftem“ und „ungeimpftem“ Blut angelegt. Wenn zu 100% ausgeschlossen werden kann, dass keine schädlichen Substanzen der Gen-Behandlung in die Blutkonserve gelangen, wäre das ja natürlich nicht nötig. Ist das so? Wenn ja, wo ist der Nachweis dazu zu finden, wie ist der aktuelle Erkenntnisstand, von wem wurden Studien dazu erarbeitet, wer hat das finanziert?
Mindestens 20% der Bevölkerung, das sind rund 16 Millionen Menschen, haben auf die Gen-Behandlung verzichtet und wollen im Ernstfall kein kontaminiertes Blut empfangen. Wie kann das Rote Kreuz belegbar und glaubhaft nachweisen, dass möglicherweise verunreinigtes Blut nicht doch in die Blutkonserven gelangt, weil sonst die Gefahr besteht, dass im Ernstfall Impfverzichter einen Schaden davontragen könnten?
Ich finde das eine wichtige Frage dem Roten Kreuz gegenüber und vielleicht wäre es auch gut, die möglichen Spender im Vorfeld für dieses heikle Thema zu sensibilisieren. Ich finde es auffällig, dass das Rote Kreuz sich hierzu weder in die eine, noch andere Richtung in den Informationen äußert, obwohl sie uns alle betrifft.
Ich schreibe diese Email aus kollegialen Gründen, aber auch zur Sensibilisierung gegenüber der Verantwortung aller Menschen gegenüber ihren Mitmenschen, die (hoffentlich nie) in die Situation kommen, einmal auf eine Blutspende angewiesen zu sein.
Wenn sich etwas Neues auf meine Nachfrage an Dich ergibt, wäre es klasse, ich würde davon erfahren.
Vielen Dank und viele Grüße
YYYYYYY
(Die Intension war, sich so vorsichtig wie möglich, quasi auf „Samtpfötchen“, an den Kern heranzupirschen. Dass es bereits Erkenntnisse dazu gibt, dass das Blut kontaminiert sein kann, wurde bewusst weggelassen, um keine Angriffsfläche zu bieten, ein „Verschwörungstheoretiker“ zu sein. Wenn die andere Seite auf einen Austausch eingestiegen wäre, wäre eine Quelle zu dieser Aussage vorhanden gewesen.)
Die Antwort:
Hallo YYYYYYY,
danke für die ausführliche Nachricht und dass du dir Gedanken zu dem Thema machst. Ich finde, man sollte Blutspenden als eine persönliche und private Sache betrachten.
Jeder und jede sollte für sich selbst abwägen, ob und unter welchen Bedingungen er oder sie das tun möchte.
Die Fragen, die du gestellt hast, sind echt speziell. Da geht's um medizinische und wissenschaftliche Themen, da kann ich als Privatperson nicht mitreden. Ich denke, dass sich Interessierte bei solchen Themen am besten direkt an medizinische Fachstellen oder das Rote Kreuz vor Ort wenden sollten, um fundierte und belastbare Informationen zu erhalten.
Mir persönlich ist es wichtig, Menschen auf die Möglichkeit der Blutspende aufmerksam zu machen.
Jeder kann das für sich selbst entscheiden und es ist auch okay, wenn man dabei Überzeugungen hat.
Beste Grüße
XXXXXXX
(„Blutspende…eine persönliche und private Sache“, nach dem Corona-Ereignis auch noch?, „…ich als Privatperson“ empfehle anderen etwas, bei dem sie möglicherweise anderen einen Schaden zufügen. Ist das schon grob fahrlässig, nach den Denkanstößen, die gegeben wurden?, „Wenn man dabei Überzeugungen hat.“, interessante Formulierung.)
Darauf die Reaktion:
Hallo XXXXXXX,
danke auch für Deine Antwort.
Wenn so eine im Grundsatz sicher gute Aktion beworben wird, liegt es nach meinem Empfinden auch in der Verantwortung, auf mögliche Folgen hinzuweisen, wenn es das Rote Kreuz schon nicht tut. Vorausgesetzt, man misst ihnen Bedeutung zu. Wenn meine E-Mail keine Veranlassung zu einer Beunruhigung und eigener Recherche angeregt hat, dann kann ich leider mehr nicht tun.
Dass das Rote Kreuz keine Hinweise gibt, liegt wohl daran, dass es Teil des Systems ist. Wer die Augen aufmacht, kann mit wenig Aufwand leider mehr als genug Tatsachenwahrheiten finden, die mit Schäden im Zusammenhang der Gen-Behandlung verursacht wurden und immer noch verursacht werden. Es ist nicht meine Aufgabe, einen Wissensrückstand von 5 Jahren auf den aktuellen Stand zu bringen. Allein die veröffentlichten RKI-Protokolle sollten schon genug Anlass zur Skepsis bieten. Der ÖRR berichtet leider nicht darüber, weil er auch Teil des Systems ist.
Ich will es damit genug sein lassen und hoffe, dass es unter den Kolleginnen und Kollegen noch weitere kritische Geister gibt.
Es geht nicht gegen Dich persönlich, aber ich hoffe, das Angebot wird nicht zahlreich genutzt.
Viele Grüße
YYYYYYY
(Einen halben Gang hochgeschaltet, ein Versuch, XXXXXXX aus der Reserve zu locken.)
Und ein Nachtrag von YYYYYYY:
Lieber XXXXXXX,
wir sind schon einmal unter Missbrauch des Begriffes „Solidarität“ hinter die Fichte geführt worden. Das darf nicht noch einmal passieren!
Nochmals viele Grüße
YYYYYYY
(Keine Reaktion mehr von XXXXXXX)
Und, wie gesagt, daraufhin kam das Video mit Bonhoeffer entgegen. Besser kann man vorsätzliche, rationale Ignoranz in Bezug auf den Schriftwechsel nicht beschreiben.
Hier wird eine jeden angehende allgemeinmedizinische Frage zu einer Frage der persönlichen Überzeugung gemacht. Das kommt doch sehr bekannt vor, oder?
Sehr wahrscheinlich lässt es sich vermuten, dass es sich bei XXXXXXX wohl um einen Corona-Jünger handelt, der die Tatsachen scheut, wie der Teufel das Weihwasser. Bloß nicht nachdenken, bloß nicht in Frage stellen, bloß nicht hellhörig oder gar neugierig werden, bloß nicht auf die Äußerungen eingehen, bloß nicht konkret werden, bloß keine eindeutig formulierte Stellung zu den Aussagen beziehen. „Angriffsfläche“ wäre vorhanden gewesen.
Das vorsichtige Anpirschen war alles andere, als mit-der-Brechstange-herangehen. Und doch setzt sofort automatisch der Teflon-Effekt ein. Selbstschutz.
Die Frage ist, wie soll da die Spaltung überwunden werden, wenn „die andere Seite“ so überhaupt nicht bereit ist, sich mit dem Vorgebrachten auseinanderzusetzen. Noch nicht einmal, wenn man nur die Spitze der Spitze des Eisbergs leise anhaucht.
Diesem Beispiel könnten viele unzählige weitere Beispiele hinzugefügt werden. Jeder hat so etwas schon einmal auf die eine oder andere Weise erlebt.
Das Gefühl lässt sich nicht unterdrücken, dass sich die Menschheit in zwei Lager aufgeteilt hat, und es gibt derzeit keinen Weg, wie man wieder aufeinander zukommen könnte.
Wie zwei Welten aufeinanderprallen, kann man derzeit auch in der Enquete-Kommission im sächsischen Landtag erleben: https://www.youtube.com/watch?v=D6ACmwBUBFM
Aus der Sicht von YYYYYYY ist das kein Grund zur Verzweiflung, jedoch drängt sich der Wunsch auf, dass man mit solchen Menschen wie XXXXXXX nichts mehr anfangen will. Man möchte mit ihnen, so schade es auch ist, am liebsten gar nichts mehr zu tun haben, und wenn doch aus irgendwelchen Gründen, nur noch das Allernotwendigste, so kurz und knapp, wie möglich. Empathie aufzubringen erscheint einem als vergeudete Energie, besser ist es, sich auf die Menschen zu konzentrieren, die wegen fehlender Genbehandlung keine Wesensveränderungen, die mittlerweile leider auch schon bestätigt sind, erlitten haben.
Wie Bonhoeffer richtig sagt, es geht hier nicht um Intelligenz, es geht viel tiefer. Es geht um das Menschsein an sich, und man hat den Eindruck, dass vor allem dies unter dem Einfluss der Spritze sehr stark gelitten hat. Da scheint so eine Abgestumpftheit durch, die einem einen kalten Schauer über den Rücken fahren lässt. Und das ist vielleicht noch gefährlicher, als diejenigen, die wirklich dumm sind. Das ist keine Arroganz oder Überheblichkeit, sondern unschuldig, wahllos von der Natur vergebene Dummheit, die jeden hätte ereilen können, hat es immer schon zu einem großen Teil gegeben. Hier hat man wenigstens noch die Möglichkeit, sich einfühlen zu können und Verständnis aufzubringen. Bei Menschen aber, von denen man weiß, dass sie die kognitiven Fähigkeiten zur Reflektion hätten, sie jedoch aus welchen Gründen auch immer nicht nutzen, oder sie als Verdrängungsmechanismus gerade nutzen, weil sie es können, geht auch eine gewisse Gefahr aus, weil man nie wissen kann, was sie sich sonst noch so ausdenken könnten, wenn sie in die geistige Enge getrieben werden, um ja nicht von Menschen, die den Mut haben, die Wahrheit auszusprechen, in ihrem mühsam aufgebauten Weltbild erschüttert zu werden. „Was nicht sein darf, das nicht sein kann!“, obwohl doch eigentlich die Wahrheit dem Menschen zumutbar ist.
So hat man das Gefühl, man atmet Honig ein und bewegt sich mühsam durch einen zähen Brei vorwärts, der einem bis zu den Oberschenkeln reicht. Jeder Schritt eine Anstrengung.
Und bevor man noch tiefer in dieses Verlustgefühl von Lebensqualität eintaucht (das hat nichts mit Depressionen zu tun, man bekommt einfach nur schlechte Laune), sich immer wieder bewusst machen, dass es da draußen noch eine Menge bei Verstand gebliebener Menschen gibt, die unermüdlich daran arbeiten, dass die Wahrheit weiter so sehr erkraftet, dass sie sich ihren Weg in den sogenannten Mainstream bahnt und die Menschen endlich aufwachen. So schmerzlich das für viele sein mag, es muss sein!
Selbst für einen wenig religiösen Menschen, im Sinne von regelmäßigen Kirchgängen und keinem Kontakt zur Institution Kirche, bekommt der Satz eine ganz besondere Bedeutung:
„Ich schicke euch den Geist der Wahrheit, und der wird euch frei machen!“
-
 @ e2c72a5a:bfacb2ee
2025-06-05 17:14:50
@ e2c72a5a:bfacb2ee
2025-06-05 17:14:50The silent revolution: Ethereum's pivot to 'digital oil' could redefine crypto's future. While Bitcoin grabs headlines as digital gold, Ethereum is quietly transforming into something potentially more valuable—the essential infrastructure powering our digital economy. Ryan Berckmans reveals Ethereum's strategic shift from being just another cryptocurrency to becoming the foundation for stablecoins, tokenized assets, and global financial systems. With $480 billion in stablecoin volume and institutional players entering the space, Ethereum isn't just competing with Bitcoin—it's creating an entirely different value proposition. The question isn't whether ETH will hit $3K, but whether we're underestimating its long-term potential as the backbone of digital finance. Are you positioning yourself for the real crypto revolution happening right under our noses?
-
 @ 2e8970de:63345c7a
2025-06-05 16:07:04
@ 2e8970de:63345c7a
2025-06-05 16:07:04https://x.com/jburnmurdoch/status/1930203297396249067
https://www.dropbox.com/scl/fi/1lp1dwzx608xdu8jfpkqk/FT_GENDER_DIVIDE_SXSW.pptx?rlkey=9gcwvn77zss3k5l5vgiquennl&e=1&st=apgyr3ug&dl=0
https://stacker.news/items/998014
-
 @ 0b884d0d:9abbd54a
2025-06-02 21:42:29
@ 0b884d0d:9abbd54a
2025-06-02 21:42:29Conceitos chaves
Neste artigo você vai entender um pouco dos conceitos chave desse novo conjunto de ferramentas para aplicar justiça de forma descentralizada e anárquica.
Antes de continuar a leitura, quero elucidar alguns termos que serão constantemente usados neste artigo.
- Private Law Society (PLS)
- Uma organização sem fins lucrativos com o objetivo de criar novas soluções para tornar cada vez mais viável a aplicabilidade de uma justiça privada e descentralizada
- Ao mesmo tempo, um conjunto de protocolos e softwares de código aberto com o mesmo propósito
- Links úteis
- Perfil Nostr: nostr:npub1p79dx59d5gctllar73cqnucqft89gpkfmydxj4mmk2jj69s7hn3sfjatxx
- GitHub: https://github.com/PrivateLawSociety
- Sobre: https://privatelawsociety.net
- Bitcoin Justice Protocol (BJP)
- Um protocolo estabelecido pela Private Law Society
- Também um software de código aberto disponível no GitHub da Private Law Society
- Links úteis
- GitHub: https://github.com/PrivateLawSociety/pls-bjp
- Sobre: https://privatelawsociety.net/bjp
- Implementação oficial da PLS: https://pls-bjp.vercel.app/
- Web Of Trust (WoT)
- Uma base de dados com avaliações entre usuários Nostr relatando confiança/desconfiança e se um usuário teve relações comerciais ou não com outro
- O objetivo é ser um repositório de reputação para chaves Nostr
- Links úteis
- GitHub: https://github.com/PrivateLawSociety/pls-wot
- Sobre: https://privatelawsociety.net/wot
- Implementação oficial da PLS: https://pls-wot.vercel.app/
- Meu fork com o grafo: https://pls-wot-kiuusai.vercel.app/
Prefácio
Recentemente saiu um episódio no BetterMoney podcast sobre o projeto de justiça privada Private Law Society.
Muitos bons pontos foram levantados neste excelente episódio pelos participantes nostr:npub12mllp29adf2fw0eeahmseczcu3y4625qyn3v4uwfvkpzlshnmj3qs903ju e nostr:npub1wsl3695cnz7skvmcfqx980fmrv5ms3tcfyfg52sttvujgxk3r4lqajteft. Mas neste entorno permanecem ainda muitas dúvidas sobre o projeto em si, seu funcionamento, princípios, objetivos e funcionalidades.
Venho através deste artigo, apresentar resumidamente o projeto, a filosofia por trás do mesmo e dar a minha visão de como este conjunto de protocolos chamado Private Law Society tem a capacidade de não só transformar o mundo como o conhecemos, mas de tornar boa parte do "poder judiciário" obsoleto e irrelevante em vários aspectos, se assim os indivíduos o quiserem.
Mas afinal, o que é essa tal de PLS?
PLS é um acrônimo para Private Law Society (Sociedade de Leis Privadas em uma tradução livre). Além de uma organização sem fins lucrativos e totalmente Open Source, trata-se de um conjunto de softwares disponíveis no GitHub de forma a estruturar um protocolo de justiça privada descentralizado com colateral em Bitcoin. Falei grego para você? Vamos com calma dissecar estes conceitos...
Sociedade de leis privadas, a "utopia" libertária se tornando realidade
Quem é adepto do movimento libertário e/ou estuda o tema, provavelmente já ouviu falar nesse termo. Originalmente cunhado por David Hume, o filósofo e idealista escocẽs. O projeto toma este nome com o intúito, talvez de forma ambiciosa, mas com certeza visionária e audaz, de trazer uma solução prática e simples de estabelecer contratos voluntários entre duas ou mais partes, as quais livremente escolhem os seus "árbitros" ou "juízes" para fazer valer a lei. Como realmente uma justiça paralela a qual o contrato faz lei entre as partes.
Para uma introdução sobre o conceito, indico este vídeo do canal AnCapSu que trata sobre o tema de forma resumida.
Essa ideia, simples a priori esbarra no problema da aplicabilidade da força, ou ao menos era o que se pensava, antes da criação de ferramentas como o Bitcoin e soluções como Taproot e Bitcoin Scripts. Agora, com uma propriedade realmente soberana, programável e incensurável, essa ideia começa a ganhar forma.
Basicamente, uma dúvida plausível para uma pessoa leiga no assunto seria: "Tá, entendi. Esse tal de bitcoin é realmente bom, seguro e o Estado não tem poder de controle sobre ele. Mas como isso pode gerar essa tal de sociedade de leis privadas? É só uma forma de dinheiro."
A resposta para isso é: Dinheiro programável, chaves privadas e reputação!
BJP: contratos colateralizados em Bitcoin
Bitcoin, Nostr e Taproot: a chave para a aplicação da justiça privada
Se você já está minimamente envolvido com o ambiente Bitcoin, Nostr e afins, deve saber o que é um par de chaves públicas e privadas e como isso funciona. Existe uma chave pública e privada, a pública é a forma de identificação no sistema e a privada é a que gera as assinaturas. Daí é possível determinar que quem publicou a mensagem, seja na blockchain do Bitcoin, seja na rede Nostr, é o dono daquela chave pública em específico. Assim, se institui uma forma de identidade digital.
O que muita gente não sabe, ou não dá o devido valor, é que depois do soft fork Taproot da rede Bitcoin (ocorrido em 2021), os antigos Bitcoin Scripts tomaram outra forma e maior capacidade, se tornando mais práticos, leves e funcionais. Isso é o que dá base hoje para "contratos inteligentes" no Bitcoin e toda a parafernalha de Ordinals, Runes e coisas do gênero. O que pra muitos foi uma maldição que encheu a mempool, na verdade também se provou uma bênção, a qual é a base do BJP (Bitcoin Justice Protocol) da Private Law Society. A atualização permitiu com que scripts mais complexos pudessem ser desenvolvidos de forma mais simples, fossem mais leves e tivessem uma melhor privacidade. O BJP se empodera disso, fornecendo uma solução ao mesmo tempo que simples, inovadora para casos de uso de contratos. Primariamente na camada nobre do Bitcoin e posteriormente na Liquid Network, para aqueles que querem poupar em taxas e terem mais privacidade.
Por sua vez, o Nostr funciona também com criptografia de curvas elípticas, assim como nosso querido Bitcoin. Para ser mais preciso, o mesmo algoritmo é usado tanto no Nostr quanto no Bitcoin. O Secp256k1. Na prática isso significa que toda chave Nostr também é uma chave Bitcoin em potencial. O BJP se apropria dessa interconexão para possibilitar a criação de contratos jurídicos.
BJP: uma multisig sofisticada?
Ok, até agora vimos o que torna esse tal de BJP possível, mas como ele funciona e como eu posso usá-lo na prática?
Bem grosseiramente falando, o BJP é um software que facilita a criação de carteiras multisig específicas para contratos jurídicos. Com ele, você constrói uma multisig não convencional com Taproot que assegura o cumprimento do contrato mediante concordância de todas as partes "clientes" do contrato ou do número mínimo de árbitros configurados previamente + um dos clientes.
Na prática, um script Taproot é montado com a seguinte lógica:
``` Clientes = {Lista de chaves públicas dos clientes}
Árbitros = {Lista de chaves públicas dos árbitros}
Quorum = Número mínimo de árbitros para aprovar a transação
Se todos os Clientes concordarem: Libera gasto Senão se 1 dentre todos os Clientes concorda e ao menos o Quorum de Árbitros concorda: Libera gasto Senão Bloqueia gasto ```
Esse algoritmo garante que o contrato seja efetuado e esteja de acordo com a vontade de todas as partes envolvidas, ou, se entrar em "disputa judicial", o número mínimo de árbitros designados para "fazer valer a lei", concorde junto com a parte lesada para onde os fundos devem ir.
Um exemplo prático:
Aqui temos um exemplo prático de aplicabilidade de um contrato feito através do BJP. Nesse caso, tendo a concordar com o nostr:npub1narc0ect9jf0ffnvcwg8kdqlte69yxfcxgxwaq35eygw42t3jqvq4hxv0r e discordar do nostr:npub12mllp29adf2fw0eeahmseczcu3y4625qyn3v4uwfvkpzlshnmj3qs903ju quando o primeiro comenta no recente episódio do BetterMoney Podcast:
19:30 Eu discordo do Júlio. Acho que a PLS seria perfeita pro contrato de aluguel. O locatário coloca o colateral e o proprietário vai ter certeza de que não vai tomar calote.
E se uma das partes tentar levar pra justiça estatal, não vai ter nenhum nome no contrato, apenas chaves públicas.
E está certo. O exemplo prático que acabei de citar reforça isso. Não há nada que impeça também, de no contrato, ter uma cláusula a qual envolver a justiça estatal cause algum prejuízo ou perda de causa imediata para a parte expositora. Não estou fazendo recomendação alguma, fazendo apologia a qualquer prática ou aconselhando usar deste tipo de artifício, se o que falo possa ser interpretado como crime pela lei positivada (não sou advogado). Mas, no campo das ideias e das possibilidades no mundo real, é uma possível solução/alternativa.
Vamos ao exemplo...
Adriano Calango quer alugar um apartamento de Beto Lagartixa. Só que ambos não se conhecem e não confiam suficientemente um no outro para fazer um contrato. Ambos decidem então escrever um documento. Word, Pdf ou um texto puro. Não importa. Lá estão todas as cláusulas, o caução do aluguel, multas estabelecidas para uso indevido, penalidades, dia de pagamento, decisão sobre multa de atraso, enfim, qualquer detalhe desse contrato.
Adriano Calango, escolhe Célsio Jacaré, seu amigo como seu árbitro pessoal. Beto Lagartixa escolhe Danilo Crocodilo, seu amigo, como seu árbitro pessoal. Ambos escolhem Eduardo Cobra, um réptil íntegro, com reputação ilibada e que já fez vários julgamentos, como um árbitro em comum para seu contrato. Daqui temos: dois contratantes, duas testemunhas e um juíz.
Adriano Calango então, acessa o site da PLS BJP para criar o contrato. Configura os clientes (ele e Beto Lagartixa), configura todos os árbitros, anexa o arquivo e cria o contrato na rede Bitcoin.
Um evento Nostr criptografado é criado e um link de compartilhamento do contrato é disponibilizado. Adriano Calango compartilha esse link com todos os usuários disponíveis.
Todos os usuários verificam os detalhes do contrato e se o documento do contrato bate com o contrato assinado. Todas as partes ativamente concordando, a nossa multisig é criada.
Um arquivo do contrato é disponibilizado para acessar a multisig do contrato posteriormente. Todos os usuários salvam esse arquivo e o mantém guardado em um local seguro. O objetivo disso é ter redundância. Se um dos participantes perder este arquivo, outro pode compartilhar o mesmo para possibilitar o acesso à multisig do contrato.
Adriano Calango e Beto Lagartixa depositam os devidos colaterais no contrato. Seja o caução de aluguel ou um montante separado para ser empenhorado. Isso é definido pelo acordo feito previamente.
Se tudo ocorrer bem, assim que Adriano Calango resolver se mudar e Beto Lagartixa não tiver nenhuma objeção quanto a isso, ambos voltam para o contrato previamente feito e concordam quanto aos montantes que cada um receberá de volta. Dividem o preço da taxa entre si e cada um tem sua propriedade de volta.
Digamos que Adriano Calango não cumpriu com parte do contrato, atrasando o pagamento de alguns meses. Por outro lado, Beto Lagartixa também não cumpriu parte de seu acordo, deixando de fornecer serviços prescritos no contrato como segurança de condomínio e um elevador funcional. O caso então é levado aos árbitros. Célsio Jacaré argumenta a favor de Adriano Calango, questionando Beto Lagartixa sobre os serviços não prestados pelo mesmo e que claramente no contrato estavam previstos como parte inclusa no custo do aluguel. Danilo Crocodio retruca sobre a inadimplência de Adriano Calango, defendendo seu amigo/cliente, Beto Lagartixa. Eduardo Cobra, ao ouvir calmamente todos os argumentos de ambos os lados, então decide: - Adriano Calango foi inadimplente por três meses. Portanto terá uma multa de 35% sobre seu patrimônio - Beto Lagartixa terá uma multa de 25% sobre o seu patrimônio, pois não prestou o serviço com a devida qualidade - O restante do patrimônio será devolvido para seus respectivos donos - Dos valores da multa: - 90% será dividido entre cada árbitro. 30% para cada - Os 10% restantes serão queimados em taxas para os mineradores
Note que não foi usado nenhum meio coercitivo para solucionar o caso e penalizar os réus em seus devidos processos. Tudo foi aceito voluntariamente previamente, inclusive da parte dos árbitros. As multas aplicadas são meramente ilustrativas. Em um cenário real, tais penalidades seriam acordadas previamente e na falta das mesmas, todas as partes discutiriam até entrar em um acordo quanto a decisão. É totalmente plausível que, por exemplo, a penalidade fosse queimar todo o valor das multas em taxas para os mineradores, se assim todos aceitassem. O mecanismo de mineração nesse cenário também se torna um possivel meio de aplicação de força em um julgamento.
Só esta parte do ecosistema já faz boa parte dos casos de uso da justiça estatal obsoleta, dando maior descentralização, privacidade e soberania para os indivíduos.
Nesse cenário temos novamente a "utopia" libertária sendo definitivamente aplicada. Não há dedo do Estado no meio, todos os contratos foram previamente acordados entre as partes e não houve violação ao PNA (Princípio da Não Agressão). Todo o processo foi estritamente voluntário desde o começo.
WoT: A digitalização da reputação
Quem vê o projeto a primeira vista, pode pensar:
Ah Calango. Legal essa solução com bitcoin e tal. Mas eu vou sempre precisar gastar meus bitcoins toda vida que fizer um contrato? Tem contratos que isso não vale a pena!
Sim. Isso é verdade. Tanto que foi genialmente um caso citado pelo nostr:npub12mllp29adf2fw0eeahmseczcu3y4625qyn3v4uwfvkpzlshnmj3qs903ju. Há casos que os valores são tão pequenos que não compensa criar todo um documento de contrato para, por exemplo, comprar um livro ou algo do tipo. Ou, algumas vezes, o próprio indivíduo não quer gastar dinheiro ou travar valores para manter esse contrato. Mas não é o único caso de uso. Lembre-se que mesmo com colaterais aplicados, normalmente as pessoas não gostam de entrar em decisões judiciais ou confusões em geral. Idealmente todos querem traçar o caminho feliz da história. Então, mesmo para firmar contratos com colateral em Bitcoin usando o BJP, é plausível que um usuário queira pesquisar o "histórico" de outro usuário na rede para averiguar se é uma boa ideia ou não se envolver com aquele indivíduo em específico.
Naturalmente o ser humano já pratica esse cálculo de reputação e analisa o ambiente a sua volta para entender a hierarquia e reputação dele e de outros indivíduos em um grupo. Somos seres sociais e naturalmente na nossa cabeça já montamos uma espécie de rede de confiança na nossa cabeça com a imagem que formamos de um indivíduo X ou Y com base na nossa comunidade. Hierarquia, lideranças, influência, são características naturais do ser humano.
A partir desse cenário, surgiu a ideia de gerar uma solução para uma melhor visualização da reputação entre usuários do protocolo. O objetivo é ser primariamente um repositório com avaliações de usuários sobre outros usuários, os classificando positivamente ou negativamente e informando se houve ou não negócios/fechamento de contratos com o mesmo. A ideia é realmente simples e o objetivo é deixar o protocolo aberto para as mais diversas formas de interpretação desses dados. Seja com modelos matemáticos, visualização e interpretação pessoal ou até mesmo o uso de inteligência artificial para o auxiliar o usuário a tomar suas decisões.
WoT: o nome é conhecido, mas a proposta é diferente
Veja que há uma diferença prática na WoT da PLS e outros projetos de WoT espalhados pela internet afora e pelo Nostr. A maioria dos projetos de WoT são para determinar se uma pessoa/chave privada é ou não relevante a partir da visão de outra chave privada. É o caso de serviços de WoT como o da Coracle.Social, Vertexlab.io e mais recentemente da nova implementação de WoT Relays. Serviços como estes tem o objetivo de reduzir ou eliminar spam e falsidade ideológica (fakes), assim como oferecer uma espécie de algoritmo de recomendação, similar ao que é feito em redes sociais como YouTube e Instagram.
Note que em nenhum momento o objetivo da WoT da PLS é definir por A + B quem é ou deixa de ser confiável ou inconfiável, afinal, confiança é algo estritamente relativo. Nenhum projeto pode ter a audácia de tentar classificar pessoas como confiáveis ou inconfiáveis a nível de estabelecimento de contratos. A PLS entende isso e respeita esse caráter subjetivo da confiança. De igual maneira, nunca foi o objetivo de qualquer projeto de WoT sério fazer algo similar ao que é feito em países como a China, onde pessoas têm alguma espécie de "crédito social". Fique tranquilo. Nosso objetivo não é tornar os episódios distópicos de Black Mirror em realidade 🤣
Visualização em grafo: uma proposta elegante
Desde que entrei de cabeça no projeto da PLS, uma coisa que veio sendo falada nas reuniões era sobre a criação de novas ferramentas para visualizar a rede de formas mais intuitivas, que ajudassem os usuários ao julgar pessoas como confiáveis ou não para estabelecer contratos, e ao mesmo tempo, resolvessem o problema de UX que é uma simples tabela com avaliações entre usuários da rede. A tendência é, a partir do momento que o projeto comece a ter adesão, que o número de notas cresça exponencialmente, e com isso, a visualização da reputação dos indivíduos seja pouco intuitiva. Uma solução apresentada para este problema foi a criação de um frontend com grafos, ou melhor, a criação de uma forma de visualização da sua rede de confiança em particular. A partir disso, foi gerada uma bounty no projeto para a implementação desta solução, a qual eu orgulhosamente estou construindo (na verdade está pronta para uso. Mas ainda quero melhorar algumas coisas). O objetivo é simples: dar ao usuário mais uma forma de contemplar os dados da WoT, de forma mais particular e intuitiva. Facilitando a tomada de decisões.
A natureza da confiança humana em sintonia com a tecnologia
Bolhas virtuais, vilarejos e mineiros
Uma possível crítica que o projeto possa receber é a possibilidade de ataques de spam ou cancelamento em massa corroer ou inviabilizar a utilidade do protocolo. Ataque Sybil também. Entretanto, são espantalhos até bem inocentes quanto ao projeto em questão.
Como havia mencionado anteriormente, a base do projeto em si é propositalmente simples e não se propõe a dar uma solução definitiva para a visualização dos dados postos no protocolo. A tabela de avaliações hoje existente no site da WoT da PLS é apenas uma das inúmeras formas de interpretar estes dados. E uma forma efetiva para problemas como esse, é justamente a implementação de uma visualização por grafo, onde os usuários podem ver redes de confiança sendo tracejadas a partir do ponto de vista específico de uma npub em particular.
Aqui a lógica de um antigo ditado é aplicada:
"O amigo do meu amigo é meu amigo"
Da mesma maneira também podemos formular outras afirmações como:
"O inimigo do meu inimigo é meu amigo"
"O inimigo do meu amigo é meu inimigo"
"O amigo do meu inimigo é meu inimigo"
Se tais derivações fazem sentido para você ou não, não cabe a mim dizer. Novamente, confiança é intrinsecamente algo de caráter subjetivo. Vai de cada um decidir quem é ou não confiável. É justamente por isso que estou implementando diversos filtros de avaliações no meu fork da PLS.
Na prática é o velho jogo de política de sempre. Como bem citado uma vez pelo filósofo e youtuber Platinho, ao citar Carl Schmitt:
Isso também se reflete na cultura mineira (e rural do Brasil em geral), por exemplo. O clássico "cê é fi de quem?". Perceba que essa é uma forma de procurar por um caminho de confiança já estabelecido. Quem tem parente em interior sabe, que uma das coisas mais comuns é os mais velhos, seja ou tio, mãe ou avô perguntar sobre um amigo que você leve para o ambiente familiar (meu filho, esse seu amigo é filho de quem?) É algo até instintivo do ser humano procurar por rotas de confiança e trabalhar de certa forma com o QI (Quem Indica). Goste você ou não, é assim que a natureza humana se expressa e é assim que a dinâmica social é montada.
Vendo que é natural a formação de bolhas, não é uma boa ideia em si interpretar os dados da WoT da PLS simplesmente de uma forma numérica bruta. A melhor forma é fazer uma abordagem individual, com base na sua rede de confiança ao invés de puramente o número de avaliações positivas e negativas.
O grafo da PLS busca justamente tornar mais intuitivo, prático e sistemático essa pesquisa natural. Essa implementação é além de uma ferramenta, uma forma de expressão social muito forte, tanto em âmbito social quanto jurídico, à medida em que a dinâmica social e jurídica se entrelaçam no tecido social.
Adriano Calango ataca novamente
Para um exemplo prático, voltemos a falar dele, Adriano Calango.
Adriano Calango conhece a WoT da PLS já faz um tempo e já avaliou todos os seus parceiros comerciais e amigos aos quais tem laços de confiança já firmes e maduros. Ele procura alguém para alugar uma casa Rolante, RS. ´Ele vê alguns perfis de síndicos no Nostr que moram na mesma cidade que ele com casas disponíveis para alugar. Mas quer ter uma noção que não está se metendo em encrenca ou lidando com algum síndico chato que inferniza a vida dos inquilinos.
Dito isso, ele acessa a WoT da PLS e vai na página do grafo. Percebe que seu amigo Bruno Jabuti, ao qual já havia avaliado positivamente anteriormente, avaliou positivamente um professor de Jiu-jitsu, conhecido como Carlos Camaleão. Que além de ser avaliado positivamente por Bruno Jabuti, recebeu várias avaliações positivas de outros usuários conhecidos de Adriano Calango. Carlos Camaleão, por sua vez, avaliou positivamente um síndico da região chamado Diego Iguana. Na descrição Carlos Camaleão descreve como em todo o tempo que ele foi inquilino de Diego Iguana sempre foi bem tratado e como seu condomínio estava sempre bem organizado e era cuidadosamente zelado, e como sempre que havia alguma falha de infraestrutura, o problema era rapidamente resolvido. Adriano Calango considera firmar um contrato de aluguel com Diego Iguana.
Assim, temos o seguinte caminho de confiança estabelecido:
Adriano Calango 👍 -> Bruno Jabuti 👍 -> Carlos Camaleão 👍 -> Diego Iguana
Passando-se alguns dias, Adriano Calango é abordado por Denis Jacaré em uma DM no Nostr oferecendo aluguel baratíssimo e com poucas exigências. Denis Jacaré foi informado que Adriano Calango estava a procura de um imóvel novo para residir. Adriano Calango, então, pega a chave Nostr de Denis Jacaré e joga na parte de "target" na página do grafo na PLS WoT. Ele percebe que Denis Jacaré tem várias avaliações negativas de inúmeros usuários, mas não consegue ainda bater o martelo quanto a confiabilidade de Denis Jacaré. Ele então insere sua própria chave Nostr no campo de "main rater" e vê que tem um caminho tracejado entre a sua npub e a de Denis Jacaré. Pra sua surpresa, ele vê que Carlos Camaleão deu a Denis Jacaré uma avaliação negativa, por conta que no período em que sua filha era inquilina do mesmo, prestou um péssimo serviço. O condomínio vivia com o elevador quebrado, a portaria muitas vezes não funcionava e tinha falta de luz constante. Denis Jacaré não tomava providẽncia nenhuma quanto a isso e ainda fazia questão de causa intriga entre os inquilinos e tentar jogar uns contra os outros. Adriano Calango, então percebe que Denis Jacaré não é confiável com base na rede de confiança definida por Adriano Calango.
Nesse caso temos o seguinte circuito estabelecido:
Adriano Calango 👍 -> Bruno Jabuti 👍 -> Carlos Camaleão 👎 -> Denis Jacaré
Adriano Calango aborda Diego Iguana para estabelecer um contrato. Agora é a vez de Diego Iguana pesquisar o histórico de Adriano Calango. Pois ele quer manter a comunidade de seu condomínio saudável e não deseja aceitar inquilinos baderneiros ou barraqueiros.
Diego Iguana faz então o caminho inverso de Adriano Calango, pondo a npub de Adriano Calango como "target" e a própria npub como "main rater". Daí Diego Iguana consegue ver que Carlos camaleão deu uma nota positiva para Bruno Jabuti e Bruno Jabuti deu uma nota positiva para Adriano Calango. Os dois então fecham negócio.
Neste exemplo, o grafo da WoT da PLS serviu como uma "bússola de confiança" para Adriano Calango e Diego Iguana firmarem um contrato no BJP com seus árbitros e advogados.
Considerações finais
Neste artigo você pôde aprender os conceitos básicos da Private Law Society, motivos de certas escolhas de design, viu exemplos práticos de casos de uso e um pouco das bases filosóficas que norteiam o ecosistema da PLS. Também pôde compreender um pouco mais sobre o conceito de WoT na PLS e como isso pode ser útil com o passar do tempo e a adesão de novos usuários no sistema.
Se este conteúdo te agregou de forma positiva em algo, considere mandar um ZAP ou fazer uma doação anônima por um dos meios disponibilizados na descrição do meu perfil Nostr. Este artigo foi feito com muito carinho e dedicação. Sua doação me encoraja a continuar produzindo e lhe mantendo informado. Se não pode ou não quer contribuir financeiramente, considere engajar no conteúdo reagindo, compartilhando e comentando. Toda a ajuda é bem vinda. Agradeço de coração sua paciência e atenção para ler até aqui.
Em breve trarei novidades sobre o desenvolvimento do grafo da WoT e logo mais, vídeo novo no meu canal do YouTube. Até mais!
-
 @ 3a7c74bb:bbdd5960
2025-06-02 11:48:00
@ 3a7c74bb:bbdd5960
2025-06-02 11:48:00- The Foundation (12th Century)
The territory that would become Portugal was originally part of the Kingdom of León and Castile. But in 1128, the young nobleman Afonso Henriques confronted his own mother at the Battle of São Mamede, taking control of the County of Portugal (Condado Portucalense).
In 1139, after winning the Battle of Ourique, he declared himself King of Portugal. Independence was recognized in 1143 by the King of León and confirmed by the Pope in 1179.
- Expansion and the discoveries (14th–16th Centuries)
In the following centuries, Portugal consolidated its territory and set out to sea. The 15th century marked the beginning of the Portuguese Discoveries:
🚢 1419–1420 – Discovery of Madeira and the Azores 🚢 1488 – Bartolomeu Dias rounds the Cape of Good Hope 🚢 1498 – Vasco da Gama reaches India 🚢 1500 – Pedro Álvares Cabral discovers Brazil
During this period, Portugal created a vast maritime empire with colonies in Africa, the Americas, Asia, and Oceania.
- Iberian Union and the restoration (1580–1640)
In 1580, after a dynastic crisis caused by the death of King Sebastian, Portugal came under Spanish rule in what is known as the Iberian Union. For 60 years, the Spanish kings ruled Portugal until, in 1640, a revolt led by John IV restored Portuguese independence.
- The decline of the Empire and the 1755 earthquake
The 18th century was marked by the Lisbon earthquake of 1755, one of the greatest disasters of its time, which destroyed much of the capital. The Marquis of Pombal led the country’s reconstruction and modernization.
The empire began to weaken, culminating in the independence of Brazil in 1822.
- Wars, republic, and dictatorship (19th–20th Centuries)
Portugal faced internal crises and took part in World War I. In 1910, the monarchy fell and the Portuguese Republic was proclaimed.
In the 20th century, the country lived under the Estado Novo dictatorship (1933–1974), led by António de Oliveira Salazar. In 1974, the Carnation Revolution brought democracy, and the following year, the last African colonies gained independence.
- Modern Portugal (21st Century)
In 1986, Portugal joined the European Union, marking a period of growth and modernization. Today, it is a democratic country with a rich culture and a history that continues to inspire the world.
- And what about the islands?
The Autonomous Regions of Madeira and the Azores play a fundamental role in Portuguese identity. Discovered in the 15th century, they have been part of Portugal ever since and have their own regional governments.
Madeira is known for its wine and stunning landscapes, while the Azores are famous for their volcanic nature and unique culture.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite writer from Madeira. Long live freedom!
-
 @ 32e18276:5c68e245
2025-06-03 14:45:17
@ 32e18276:5c68e245
2025-06-03 14:45:176 years ago I created some tools for working with peter todd's opentimestamps proof format. You can do some fun things like create plaintext and mini ots proofs. This short post is just a demo of what these tools do and how to use them.
What is OTS?
OpenTimestamps is a protocol for stamping information into bitcoin in a minimal way. It uses OP_RETURN outputs so that it has minimal impact on chain, and potentially millions of documents are stamped all at once with a merkle tree construction.
Examples
Here's the proof of the
ots.csource file getting stamped into the ots calendar merkle tree. We're simply printing the ots proof file here withotsprint:``` $ ./otsprint ots.c.ots
version 1 file_hash sha256 f76f0795ff37a24e566cd77d1996b64fab9c871a5928ab9389dfc3a128ec8296 append 2e9943d3833768bdb9a591f1d2735804 sha256 | --> append 2d82e7414811ecbf | sha256 | append a69d4f93e3e0f6c9b8321ce2cdd90decd34d260ea3f8b55e83d157ad398b7843 | sha256 | append ac0b5896401478eb6d88a408ec08b33fd303b574fb09b503f1ac1255b432d304 | sha256 | append 8aa9fd0245664c23d31d344243b4e8b0 | sha256 | prepend 414db5a1cd3a3e6668bf2dca9007e7c0fc5aa6dc71a2eab3afb51425c3acc472 | sha256 | append 5355b15d88d4dece45cddb7913f2c83d41e641e8c1d939dac4323671a4f8e197 | sha256 | append a2babd907ca513ab561ce3860e64a26b7df5de117f1f230bc8f1a248836f0c25 | sha256 | prepend 683f072f | append 2a4cdf9e9e04f2fd | attestation calendar https://alice.btc.calendar.opentimestamps.org | --> append 7c8764fcaba5ed5d | sha256 | prepend f7e1ada392247d3f3116a97d73fcf4c0994b5c22fff824736db46cd577b97151 | sha256 | append 3c43ac41e0281f1dbcd7e713eb1ffaec48c5e05af404bca2166cdc51966a921c | sha256 | append 07b18bd7f4a5dc72326416aa3c8628ca80c8d95d7b1a82202b90bc824974da13 | sha256 | append b4d641ab029e7d900e92261c2342c9c9 | sha256 | append 4968b89b02b534f33dc26882862d25cca8f0fa76be5b9d3a3b5e2d77690e022b | sha256 | append 48c54e30b3a9ec0e6339b88ed9d04b9b1065838596a4ec778cbfc0dfc0f8c781 | sha256 | prepend 683f072f | append 8b2b4beda36c18dc | attestation calendar https://bob.btc.calendar.opentimestamps.org | --> append baa878b42ef3e0d45b324cc3a39a247a | sha256 | prepend 4fb1bc663cd641ad18e5c73fb618de1ae3d28fb5c3c224b7f9888fd52feb09ec | sha256 | append 731329278830c9725497d70e9f5a02e4b2d9c73ff73560beb3a896a2f180fdbf | sha256 | append 689024a9d57ad5daad669f001316dd0fc690ac4520410f97a349b05a3f5d69cb | sha256 | append 69d42dcb650bb2a690f850c3f6e14e46c2b0831361bac9ec454818264b9102fd | sha256 | prepend 683f072f | append bab471ba32acd9c3 | attestation calendar https://btc.calendar.catallaxy.com append c3ccce274e2f9edfa354ec105cb1a749 sha256 append 6297b54e3ce4ba71ecb06bd5632fd8cbd50fe6427b6bfc53a0e462348cc48bab sha256 append c28f03545a2948bd0d8102c887241aff5d4f6cf1e0b16dfd8787bf45ca2ab93d sha256 prepend 683f072f append 7f3259e285891c8e attestation calendar https://finney.calendar.eternitywall.com ```
The tool can create a minimal version of the proofs:
``` $ ./otsmini ots.c.ots | ./otsmini -d | ./otsprint
version 1 file_hash sha256 f76f0795ff37a24e566cd77d1996b64fab9c871a5928ab9389dfc3a128ec8296 append 2e9943d3833768bdb9a591f1d2735804 sha256 append c3ccce274e2f9edfa354ec105cb1a749 sha256 append 6297b54e3ce4ba71ecb06bd5632fd8cbd50fe6427b6bfc53a0e462348cc48bab sha256 append c28f03545a2948bd0d8102c887241aff5d4f6cf1e0b16dfd8787bf45ca2ab93d sha256 prepend 683f072f append 7f3259e285891c8e attestation calendar https://finney.calendar.eternitywall.com ```
which can be shared on social media as a string:
5s1L3tTWoTfUDhB1MPLXE1rnajwUdUnt8pfjZfY1UWVWpWu5YhW3PGCWWoXwWBRJ16B8182kQgxnKyiJtGQgRoFNbDfBss19seDnco5sF9WrBt8jQW7BVVmTB5mmAPa8ryb5929w4xEm1aE7S3SGMFr9rUgkNNzhMg4VK6vZmNqDGYvvZxBtwDMs2PRJk7y6wL6aJmq6yoaWPvuxaik4qMp76ApXEufP6RnWdapqGGsKy7TNE6ZzWWz2VXbaEXGwgjrxqF8bMstZMdGo2VzpVuEyou can even do things like gpg-style plaintext proofs:
``` $ ./otsclear -e CONTRIBUTING.ots -----BEGIN OPENTIMESTAMPS MESSAGE-----
Email patches to William Casarin jb55@jb55.com
-----BEGIN OPENTIMESTAMPS PROOF-----
AE9wZW5UaW1lc3RhbXBzAABQcm9vZgC/ieLohOiSlAEILXj4GSagG6fRNnR+CHj9e/+Mdkp0w1us gV/5dmlX2NrwEDlcBMmQ723mI9sY9ALUlXoI//AQRXlCd716J60FudR+C78fkAjwIDnONJrj1udi NDxQQ8UJiS4ZWfprUxbvaIoBs4G+4u6kCPEEaD8Ft/AIeS/skaOtQRoAg9/jDS75DI4pKGh0dHBz Oi8vZmlubmV5LmNhbGVuZGFyLmV0ZXJuaXR5d2FsbC5jb23/8AhMLZVzYZMYqwjwEPKWanBNPZVm kqsAYV3LBbkI8CCfIVveDh/S8ykOH1NC6BKTerHoPojvj1OmjB2LYvdUbgjxBGg/BbbwCGoo3fi1 A7rjAIPf4w0u+QyOLi1odHRwczovL2FsaWNlLmJ0Yy5jYWxlbmRhci5vcGVudGltZXN0YW1wcy5v cmf/8Aik+VP+n3FhCwjwELfTdHAfYQNa49I3CYycFbkI8QRoPwW28AgCLn93967lIQCD3+MNLvkM jiwraHR0cHM6Ly9ib2IuYnRjLmNhbGVuZGFyLm9wZW50aW1lc3RhbXBzLm9yZ/AQ3bEwg7mjQyKR PykGgiJewAjwID5Q68dY4m+XogwTJx72ecQEe5lheCO1RnlcJSTFokyRCPEEaD8Ft/AIw1WWPe++ 8N4Ag9/jDS75DI4jImh0dHBzOi8vYnRjLmNhbGVuZGFyLmNhdGFsbGF4eS5jb20= -----END OPENTIMESTAMPS PROOF-----
$ ./otsclear -v <<<proof_string... # verify the proof string ```
I've never really shared these tools before, I just remembered about it today. Enjoy!
Try it out: https://github.com/jb55/ots-tools
-
 @ 58537364:705b4b85
2025-06-05 15:55:12
@ 58537364:705b4b85
2025-06-05 15:55:12อารมณ์ คือ โลก - โลก คือ อารมณ์ อารมณ์ ในโลกปัจจุบันรวมอยู่ที่ วัตถุนิยม อารมณ์ จึงเป็นปัจจัยแห่งเหตุการณ์ทุกอย่างในโลก
…. “ เดี๋ยวนี้คําว่า “อารมณ์” ในภาษาไทยนั้น หมายถึงความรู้สึกในใจมากกว่า; เช่น พื้นเพของจิตใจในขณะนั้นเป็นอย่างไร, เรียกว่าอารมณ์ของเขาเป็นอย่างไร, อารมณ์กําลังดี อารมณ์กําลังไม่ดี, นี่ คําว่าอารมณ์ในภาษาไทยใช้กันไปเสียอย่างนี้ ; มันคนละเรื่องกับในภาษาบาลี ซึ่งคําว่า “อารมณ์” หมายถึง สิ่งที่จะเข้ามากระทบ ตา หู จมูก ลิ้น กาย ใจ.
…. ถ้ากระทบแล้วเกิดความรู้สึกอย่างไร งุ่นง่านอยู่ในใจ อันนั้นไม่ได้เรียกว่าอารมณ์; อันนั้นก็เรียกว่ากิเลสอย่างอื่น เช่น เรียกว่าตัณหาบ้าง อุปาทานบ้าง; ถ้าจัดเป็นพวกขันธ์ ก็เรียกว่า เวทนาขันธ์บ้าง สัญญาขันธ์บ้าง สังขารขันธ์บ้าง; ถ้าเป็นความคิดที่งุ่นง่านก็เรียกว่า “สังขารขันธ์” ทั้งนั้น ดังนั้น เราจะต้องถือเอาคําว่าอารมณ์ในบาลีมาเป็นหลัก …. คําว่า อารมณ์ ที่จะเข้าใจกันง่ายๆ ก็หมายความว่า รูป เสียง กลิ่น รส โผฏฐัพพะ ที่จะมากระทบ ตา หู จมูก ลิ้น กาย นี้ ๕ อย่าง แล้วก็ความรู้สึกเก่าแก่ที่จะมาผุดขึ้นในใจอีก เรียกว่า ธัมมารมณ์ ที่จะมากระทบใจในปัจจุบันนี้ นี้ก็เป็นอันหนึ่ง เลยได้เป็นอารมณ์ ๖. อารมณ์กระทบ ตา หู จมูก ลิ้น กาย ๕ อย่างข้างนอกนี้ก็สําคัญไปพวกหนึ่ง ที่ปรุงขึ้นภายในสําหรับกระทบใจโดยไม่ต้องอาศัย ตา หู จมูก ลิ้น กาย ใจ เลย ในเวลานั้นก็ยังมีอยู่นี้เรียกว่าธัมมารมณ์ นี้ก็ยิ่งสําคัญ: แต่ว่ารวมกันแล้วก็เรียกว่า อารมณ์ ได้ด้วยกันทั้งนั้น แปลว่า สิ่งที่จะมากระทบกับ ตา หู จมูก ลิ้น กาย ใจ นั่นเอง
…. นี้ ดูให้ละเอียดตามตัวหนังสือ คําว่า “อารมณ์” แปลว่า ที่หน่วงบ้าง แปลว่า ที่ยินดีบ้าง, มันมีความหมายละเอียดมาก. ถ้าถือเอาความหมายอย่างคนที่มีตัวตนเป็นหลัก ธรรมะในฝ่ายฮินดูหรือฝ่ายพรหมณ์เขาก็จะพูดว่า สําหรับจิตหรืออาตมันเข้าไปจับฉวยเอา. แต่ถ้าพูดอย่างภาษาชาวพุทธพูดอย่างนั้นไม่ได้ เพราะไม่มีจิตไม่มีอาตมันชนิดนั้น แล้วจิตนี้ก็เพิ่งเกิดขึ้นหลังอารมณ์กระทบแล้ว; เลยต้องพูดตามพระบาลีที่ว่า อาศัยตาด้วย อาศัยรูปด้วย ย่อมเกิดจักษุวิญญาณ; ตาอาศัยกับรูปคืออารมณ์นั้นได้แล้วจึงจะเกิดจักษุวิญญาณ วิญญาณหรือจิตนี้เกิดทีหลัง
…. ฉะนั้น จึงไม่พูดว่า อารมณ์นี้เป็นสิ่งสําหรับจิตหรือตัวตนเข้าไปจับฉวยยึดเอา; ถ้าพูดอย่างนั้นมันก็จะเป็นฮินดูหรือพราหมณ์ไป คือมีตัวตนไป. พูดอย่างพุทธไม่มีตัวตน ทุกอย่างไม่ใช่ตัวตน เป็นสักว่าธาตุ, ได้การปรุงแต่งที่เหมาะแล้วมันก็ปรุงแต่งเป็นสิ่งใหม่ขึ้นมา ในนั้นอาจจะมีความรู้สึกโง่ไปว่าเป็นตัวเราก็ได้
…. ฉะนั้น คําว่าอารมณ์ ถ้าถือตามหลักในทางพุทธศาสนา ก็แปลว่า สิ่งที่อาศัยกันกับจิต จะเรียกว่าเป็นที่หน่วงของจิตมันก็ยังได้: ถ้าเข้าใจผิดมันก็ผิดได้: เรียกว่าสิ่งที่อาศัยกับอายตนะ แล้วก็เกิดเป็นความรู้สึกเป็นจิตขึ้นมา จิตกําลังหน่วงสิ่งนั้นเป็นอารมณ์ก็ได้ แต่จะให้เป็นตัวตนนั้นไม่ได้
…. โดยพยัญชนะก็มีอยู่อย่างนี้ ตัวพยัญชนะก็ยังกํากวม อารมฺมณํ หรือที่มาจาก อาลมฺพนํ ก็แปลว่า ที่หน่วงของจิต. ถ้าจะถือว่ามาจาก รม ที่แปลว่า ยินดี ก็แปลว่า มันเป็นสิ่งที่หลงใหลยินดีของจิต อย่างนี้ก็ยังได้อีก
…. แต่ขอให้รู้จักจากภายในดีกว่าที่จะมารู้จักจากตัวหนังสือ เมื่อตากระทบรูป เมื่อหูกระทบเสียง เป็นต้น มันเกิดขึ้นในใจ, แล้วสังเกตเอาที่นั่นก็แล้วกัน ว่ารูปที่มากระทบตานั้นมันคืออะไร? เสียงที่มากระทบหูนั้นมันคืออะไร? จะค่อยเข้าใจแจ่มแจ้งขึ้นทีละน้อยๆ ว่าอารมณ์นั้นคืออะไร? แต่ให้เข้าใจไว้ทีหนึ่งก่อนว่าสิ่งที่เรียกว่าอารมณ์ๆที่มากระทบนี้ มันยังไม่ดีไม่ชั่ว ยังไม่จัดเป็นสิ่งดีสิ่งชั่ว มันต้องผสมปรุงแต่งเป็นความคิดอย่างนั้นอย่างนี้เสียก่อน จึงจะจัดเป็นดีเป็นชั่ว อารมณ์ล้วนๆยังไม่ดีไม่ชั่ว จะได้รู้จักป้องกัน อย่าให้เป็นไปในทางชั่ว, ให้เป็นไปแต่ในทางดีได้ตามปรารถนา
…. นี้เรียกว่าโดยพยัญชนะ โดยตัวหนังสือ คําว่า “อารมณ์” แปลว่า เป็นที่ยินดีแห่งจิต, เป็นที่ยึดหน่วงแห่งจิต; โดยเฉพาะภาษาอภิธรรมแล้วก็ใช้คําว่า “เป็นที่หน่วงเอาของจิต”, คือจิตย่อมหน่วงสิ่งใดสิ่งหนึ่งเป็นอารมณ์ แปลคําว่าอารมณ์บ้าง, อาลัมพนะ แปลว่า เป็นที่หน่วงเอา.
…. เดี๋ยวนี้เราเรียนพุทธศาสนาไม่ใช่เรามาเรียนหนังสือบาลี, เราจะเรียนพระธรรมคําสอนของพระพุทธเจ้า เราก็ต้องดูสิ่งที่เรียกว่าอารมณ์ โดยหลักของธรรมชาติที่ปรุงแต่งกันอยู่ในใจดีกว่า; ก็อย่างพระบาลีที่ได้ว่ามาแล้วข้างต้นว่า จกฺขุญฺจ ปฏิจฺจ รูเป จ อุปฺปชฺชติ จกฺขุวิญฺญาณํ = เพราะอาศัยตาด้วย รูปด้วย ย่อมบังเกิดจักษุวิญญาณ ติณฺณํ ธมฺมานํ สงฺคติ ผสฺโส - การประจวบกันของ ๓ สิ่งนี้เรียกว่า “ผัสสะ”, ผสฺสปจฺจยา เวทนา = เพราะผัสสะเป็นปัจจัยจึงเกิดเวทนา, อย่างนี้เรื่อยไปจนเกิดทุกข์ จนเกิดความทุกข์, นี้เรียกว่าโดยธรรมชาติ
…. สิ่งที่เรียกว่าอารมณ์มีอยู่โดยธรรมชาติที่จะเข้ามาอาศัยกันกับตาข้างใน ที่มีอยู่ในตัวคน. แล้วจะเกิดจักษุวิญญาณ เป็นต้น ขึ้นในตัวคน; จะเกิด ผัสสะ เวทนา ตัณหา อุปาทาน ภพ ชาติ ขึ้นในตัวคน; นี้โดยธรรมชาติ พระพุทธเจ้าท่านบันดาลอะไรไม่ได้ : ธรรมชาติเป็นอยู่อย่างนี้ แต่ท่านรู้เรื่องนี้ท่านจึงนํามาสอนว่า ธรรมชาติมันมีอยู่อย่างนี้ เราจะต้องเข้าใจให้ถูกต้อง โดยที่จะป้องกันความทุกข์ไม่ให้เกิดขึ้นมาได้, หรือถ้าเกิดขึ้นมาได้ก็จะดับเสียได้
…. เราควรจะรู้จักอารมณ์ในฐานะที่เป็นธรรมชาติอันหนึ่ง ที่มีอยู่ตามธรรมชาติ แล้วที่จะเข้ามาทําเรื่องทําราวขึ้นในจิตใจของคนเราให้เกิดปัญหายุ่งยากนี้ให้ดีๆ นี้เรียกว่ารู้จักอารมณ์จากธรรมชาติโดยตรงอย่างนี้ ดีกว่าที่จะรู้จักตามตัวหนังสือ, ดีกว่าที่จะรู้จักตามคําบอกเล่าบางอย่างบางประการที่มันไม่มีประโยชน์อะไร. รู้จักตามคําบอกเล่าก็รู้จักตามที่พระพุทธเจ้าท่านตรัสดีกว่า แต่แล้วยังไม่รู้จักตัวจริง จนกว่าจะมารู้จักจากที่เมื่ออารมณ์มากระทบตา หู จมูก ลิ้น กาย ใจ เข้าจริงๆ : นั่นจึงจะรู้จักอารมณ์ รู้จักผลที่เกิดขึ้นจากการกระทบของอารมณ์, รู้จักต่อไปตามลําดับ จนแก้ปัญหาต่างๆ ได้
…. นี่ ขอร้องให้รู้จักสิ่งที่เรียกว่า อารมณ์ ในฐานะที่เป็นธรรมชาติอันหนึ่ง ที่มีอยู่ตามธรรมชาติ ที่จะเข้ามากระทบอายตนะภายใน คือ กระทบ ตา หู จมูก ลิ้น กาย ใจ แล้วมีเรื่องมีราวมีปัญหา
อารมณ์ คือ โลก - โลก คือ อารมณ์ …. “ ที่นี้จะให้ดูต่อไปอีก ว่าโดยข้อเท็จจริงที่เป็นอยู่แล้ว อารมณ์นั้นคืออะไร? ถ้าจะพูดโดยข้อเท็จจริงหรือตามสถานการณ์ที่เป็นอยู่จริงในชีวิตของคนเรา อารมณ์มันก็คือ “โลก” นั่นเอง. เดี๋ยวนี้เราไม่รู้จักโลกในฐานะอย่างนี้, เราไปเข้าใจความหมายของคําว่าโลกแคบไปบ้าง หรือว่าเขวไปบ้าง.
…. ถ้าจะรู้ตามหลักพระพุทธศาสนาแล้ว โลกทั้งหมดก็คือสิ่งที่จะมาปรากฏแก่ ตา หู จมูก ลิ้น กาย ใจ ของเรา, เรามีเพียง ๖ อย่าง, แล้วมันก็ ปรากฏได้เพียง ๖ ทาง, มากกว่านั้นมันปรากฏไม่ได้ ดังนั้น โลกก็คือสิ่งที่จะมาปรากฏแก่ ตา หู จมูก ลิ้น กาย ใจ ๖ อย่างของเรา. “โลก” ก็คือ รูป เสียง กลิ่น รส โผฏฐัพพะ ธัมมารมณ์ ๖ ประการเท่านั้น, ไม่มีอะไรมากไปกว่านั้น
…. ฉะนั้น รูป เสียง กลิ่น รส โผฏฐัพพะ ธัมมารมณ์ แต่ละอย่าง ๆ ก็คือ โลกในแต่ละแง่ละมุม นั่นเอง, ที่เป็น รูป เสียง กลิ่น รส โผฏฐัพพะ ก็อยู่ข้างนอก จะเรียกว่าอยู่ข้างนอกก็ได้, ที่เป็นอารมณ์เกิดขึ้นในใจ ปรุงขึ้นในใจก็เรียกว่าโลกข้างในก็ได้ แต่มันก็เป็นโลกอยู่นั่นแหละ เพราะมันเป็นสิ่งที่จิตจะต้องรู้สึก จิตรู้สึกก็เรียกว่าโลกสําหรับจิต ตา หู จมูก ลิ้น กาย รู้สึก ก็เรียกว่าโลกสำหรับ ตา หู จมูก ลิ้น กาย. นี้ขอให้มองให้เห็นชัดตามพระพุทธประสงค์ว่า โลก ก็คือ อารมณ์, อารมณ์ ก็คือ โลก.
…. แต่ทีนี้ พระพุทธเจ้าท่านมองลึกกว่านั้น ท่านตรัสถึงข้อที่ว่า ถ้ามันมาเกิดเป็นปัญหาแก่เราเมื่อไรจึงจะเรียกว่า “มันมี” พอมันมาเป็นปัญหาแก่เราเมื่อไรก็เรียกว่า “เป็นทุกข์”; เพราะว่าเราได้ไปจับฉวยยึดถือเอาตามประสาตามวิสัยของคนที่ไม่รู้จักโลก ถ้าพูดว่าไม่รู้จักโลกแล้วคนก็มักจะไม่ยอมรับ เพราะว่าเขาจะพูดว่าเขารู้จักโลกดี. ยิ่งพวกฝรั่งสมัยนี้ นักวิทยาศาสตร์ปราดเปรื่องนั้น เขาจะไม่ยอมรับว่าเขาไม่รู้จักโลก. แต่ถ้าพูดตามหลักพุทธศาสนาแล้วก็จะพูดได้ว่ายังไม่รู้จักโลกเลย เป็นคนตาบอดยิ่งกว่าตาบอด; เพราะว่าฝรั่งเหล่านั้นรู้จักโลกแต่ในแง่สําหรับจะยึดมั่นถือมั่นเป็น “ตัวกู ของกู” จะครองโลกจะอะไร เอาประโยชน์ทุกอย่าง; เขารู้จักโลกในแง่นี้ อย่างนี้พุทธบริษัทไม่เรียกว่า “รู้จักโลก”; แต่ถือว่าเป็นคนตาบอดต่อโลก, หลงยึดมั่นถือมั่นในโลก. เพราะว่าคนเหล่านั้นไม่รู้จักโลกโดยความเป็นอารมณ์ ๖ ประการ คือ รูป เสียง กลิ่นรส โผฏฐัพพะ ธัมมารมณ์, แล้วเป็น “มายา” คือ เอาจริงไม่ได้ เป็นของชั่วคราวๆ หลอกให้เกิดความรู้สึกยึดมั่นถือมั่น
…. นี้เรารู้จัก เราไม่ไปหลงยึดมั่นถือมั่นกับมัน นี้จึงเรียกว่า “คนที่รู้จักโลก” ไปตามหลักของพุทธศาสนา, ฉะนั้น จึงไม่ยึดมั่นถือมั่นสิ่งใดโดยความเป็นตัวตน หรือโดยความเป็นของตน, เรียกว่าเป็นผู้รู้จักอารมณ์ ๖ ประการนั้นก็คือรู้จักโลกทั้งปวง, แล้วก็ไม่หลงไปในโลกในแง่ใดแง่หนึ่ง นี้เรียกว่า อารมณ์ ก็คือ โลก นั่นเอง ในความหมายที่ลึกที่สุดของพระพุทธสาสนา ไม่ใช่โลกก้อนดิน, ไม่ใช่โลกก้อนกลมๆ นี้. แต่มันหมายถึงคุณค่าอะไรที่มันมีอยู่ในโลกกลมๆ นี้ ที่จะเข้ามามาทําให้เกิดปัญหา ที่ตา ที่หู ที่จมูก ที่ลิ้น ที่กาย ที่ใจ ของคน. นั่นแหละคือตัวร้ายกาจของสิ่งที่เรียกว่า โลก เราจะต้องรู้จักในส่วนนี้ให้เพียงพอ
อารมณ์ในโลกปัจจุบันมารวมที่วัตถุนิยม …. ทีนี้ ดูอีกแง่หนึ่งก็โดยปัญหาที่กําลังมีอยู่ อารมณ์ในโลกนี้ในฐานะที่มันเป็นตัวปัญหาที่กําลังมีอยู่ มันมารวมอยู่ที่คําว่า “วัตถุนิยม”: หมายความว่า ตา หู จมูก ลิ้น กาย ใจ นี้ มันเป็นฝ่ายชนะ ไปหลงใหลในอารมณ์ รูป เสียง กลิ่น รส โผฏฐัพพะ ฯลฯ, แล้วก็เกิดนิยมหลงใหลในวัตถุเหล่านั้น จนเกิดความคิดใหม่ๆ, ปรุงแต่งไปในทางที่จะให้หลงใหลในโลกยิ่งขึ้นๆ, ความเจริญก้าวหน้า ในโลกสมัยนี้เป็นไปแต่ในทางอย่างนี้ ฉะนั้น จึงไกลความสงบ, ไกลสันติภาพ ไกลอะไรออกไปทุกที. การที่มนุษย์ที่มีปัญญาในโลกสมัยนี้ โดยเฉพาะฝรั่งที่ก้าวหน้านั้นเขาก็จัดโลกไปแต่ในแง่ของวัตถุมากขึ้นๆ: มันก็ไกลจากสันติภาพ ไกลจากความสงบสุขยิ่งขึ้นทุกที
…. ความสะดวกสบายที่ทําให้เกิดขึ้นมาได้นั้น ไม่ได้ช่วยส่งเสริมเกิดสันติภาพ; แต่มันช่วยให้เกิดความหลงในโลกนั้นเองมากขึ้น แล้วก็ช่วยให้หลงใหลใน “ตัวกู ของกู”, ยึดมั่นถือมั่นเห็นแก่ตัวมากขึ้น รวมกันแล้วมันไม่มีทางที่จะเกิดสันติภาพหรือสันติสุขในโลกได้เลย, จึงกลายเป็นความหลอกลวงเหลือประมาณ โลกจึงกลายเป็นความหลอกลวง, หรือสิ่งที่หลอกลวงเหลือประมาณใน เวลานี้ เราเรียกกันว่า ติดบ่วง หรือว่า ติดเหยื่อของวัตถุนิยม. คําพูดทั้งหมดนี้ ล้วนแต่เป็นการแสดงให้เห็นว่า อารมณ์นี้คืออะไร สิ่งที่เรียกว่าอารมณ์นั้น คือตัวโลกที่กําลังหลอกลวงเราอยู่ทุกวันอย่างยิ่ง โดยเฉพาะในปัจจุบันนี้เป็นวัตถุนิยม นี้คืออารมณ์”
พุทธทาสภิกขุ ที่มา : ธรรมบรรยายภาคมาฆบูชา ครั้งที่ ๗ หัวข้อเรื่อง “อารมณ์ คือ ปัจจัยแห่งเหตุการณ์ทุกอย่างในโลก” เมื่อวันที่ ๑๖ กุมภาพันธ์ ๒๕๑๗ จากหนังสือชุดธรรมโฆษณ์ เล่มชื่อว่า “ก ข ก กา ของการศึกษาพุทธศาสนา”
หมายเหตุ
“อารมณ์ ” ในทางพุทธศาสนา มี ๖ คือ... * ๑. รูปะ = รูป, สิ่งที่เห็น หรือ วัณณะ คือ สี * ๒. สัททะ = เสียง * ๓. คันธะ = กลิ่น * ๔. รสะ = รส * ๕. โผฏฐัพพะ = สัมผัสทางกาย * ๖. ธรรมารมณ์ = สิ่งที่ใจนึกคิด, อารมณ์ที่เกิดกับใจ
…. ทั้ง ๖ อย่างนี้ เป็นสิ่งสำหรับให้จิตยึดหน่วง เรียกอีกอย่างว่า "อายตนะภานนอก" ก็ได้
“อายตนะภายใน ๖” คือ ที่เชื่อมต่อให้เกิดความรู้, แดนต่อความรู้ฝ่ายภายใน มี * ๖ อย่าง คือ... * ๑. จักษุ - ตา * ๒. โสตะ - หู * ๓. ฆานะ - จมูก * ๔. ชิวหา - ลิ้น * ๕. กาย - กาย * ๖. มโน - ใจ
… หรือจะเรียกอีกอย่างว่า “อินทรีย์ ๖” ก็ได้ เพราะเป็นใหญ่ในหน้าที่ของตนแต่ละอย่าง เช่น จักษุ เป็นเจ้าการ(เป็นใหญ่)ในการเห็น เป็นต้น
ท. ส. ปัญญาวุฑโฒ – รวบรวม.
-
 @ e2c72a5a:bfacb2ee
2025-06-05 17:11:03
@ e2c72a5a:bfacb2ee
2025-06-05 17:11:03The $220 million crypto heist that took just minutes reveals a fatal flaw in DeFi security. While blockchain tech promises trustless transactions, the Cetus DEX exploit on Sui exposed how a single undetected bug in a math library became catastrophic. What's truly alarming isn't the hack itself but the revelation from Curve's founder that professional hackers-for-hire are now coordinating sophisticated cross-platform attacks. This signals a dangerous evolution in crypto threats where vulnerabilities aren't just discovered—they're hunted by organized teams with specialized skills. The industry faces a stark choice: invest aggressively in preventative security or watch as billions more vanish in seconds. Is your crypto truly safe, or just waiting for the right hacker to find its weakness?
-
 @ b83a28b7:35919450
2025-05-16 19:26:56
@ b83a28b7:35919450
2025-05-16 19:26:56This article was originally part of the sermon of Plebchain Radio Episode 111 (May 2, 2025) that nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpqtvqc82mv8cezhax5r34n4muc2c4pgjz8kaye2smj032nngg52clq7fgefr and I did with nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7ct4w35zumn0wd68yvfwvdhk6tcqyzx4h2fv3n9r6hrnjtcrjw43t0g0cmmrgvjmg525rc8hexkxc0kd2rhtk62 and nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpq4wxtsrj7g2jugh70pfkzjln43vgn4p7655pgky9j9w9d75u465pqahkzd0 of the nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcqyqwfvwrccp4j2xsuuvkwg0y6a20637t6f4cc5zzjkx030dkztt7t5hydajn
Listen to the full episode here:
<<https://fountain.fm/episode/Ln9Ej0zCZ5dEwfo8w2Ho>>
Bitcoin has always been a narrative revolution disguised as code. White paper, cypherpunk lore, pizza‑day legends - every block is a paragraph in the world’s most relentless epic. But code alone rarely converts the skeptic; it’s the camp‑fire myth that slips past the prefrontal cortex and shakes hands with the limbic system. People don’t adopt protocols first - they fall in love with protagonists.
Early adopters heard the white‑paper hymn, but most folks need characters first: a pizza‑day dreamer; a mother in a small country, crushed by the cost of remittance; a Warsaw street vendor swapping złoty for sats. When their arcs land, the brain releases a neurochemical OP_RETURN which says, “I belong in this plot.” That’s the sly roundabout orange pill: conviction smuggled inside catharsis.
That’s why, from 22–25 May in Warsaw’s Kinoteka, the Bitcoin Film Fest is loading its reels with rebellion. Each documentary, drama, and animated rabbit‑hole is a stealth wallet, zipping conviction straight into the feels of anyone still clasped within the cold claw of fiat. You come for the plot, you leave checking block heights.
Here's the clip of the sermon from the episode:
nostr:nevent1qvzqqqqqqypzpwp69zm7fewjp0vkp306adnzt7249ytxhz7mq3w5yc629u6er9zsqqsy43fwz8es2wnn65rh0udc05tumdnx5xagvzd88ptncspmesdqhygcrvpf2
-
 @ fbf0e434:e1be6a39
2025-06-05 14:08:24
@ fbf0e434:e1be6a39
2025-06-05 14:08:24Hackathon 概要
ETHBratislava Hackathon Vol.2 汇聚 54 名开发者并审核通过 11 个项目,成为以太坊社区的重要盛事。此次黑客马拉松在斯洛伐克技术大学举办,参与者可免费参与 ETHBratislava 大会,这一安排助力开发者探索区块链技术的前沿进展。
项目在解决以太坊可扩展性与互操作性问题上成果显著,尤其在 “World Computer” 赛道表现突出。“Zircuit Restaking Track” 赛道也带来重要创新,聚焦通过 AI 驱动的 zk rollups 技术提升安全性与扩展性。“European Stablecoin EURØP Challenge” 则致力于开发欧元背书的稳定币,推动欧洲监管数字货币概念落地。
参与者不仅获得资深导师指导、与行业领袖建立连接的机会,现场更有招聘方挖掘技术人才。活动在兼具庆祝与社交属性的派对中落幕。总计 4,000 欧元奖金的设置,营造了开发者之间竞争与合作并存的创新氛围。ETHBratislava Vol.2 成功孵化出影响以太坊未来的创新构想,同时强化了社区联结。
Hackathon 获奖者
World Computer 奖项获奖者
此类别着重于利用以太坊能力的面向消费者的应用程序。开发者创建了解决方案,旨在增强包容性、金融工具和教育平台。获奖者包括:
- Zhar: 该去中心化平台使用AI和以太坊区块链来管理、执行和激励使用智能合约和代币的链上挑战。
- Ledger Lens: 一个Web应用程序,促进对以太坊多层生态系统的可视化和分析,强调代币流动和跨链桥使用等指标。
现实世界代币化奖项获奖者
此类别集中于在欧洲利用EUR锚定的稳定币EURØP构建效用。项目目标是在此数字货币之上部署初步技术增强。
- dEST: 一个去中心化平台,利用NFTs和智能合约来促进无中介的代币化房地产交易。
- EnergyHub: 一个提供去中心化平台以货币化多余绿色能源并通过智能合约和用户友好的仪表板实现能源捐赠的应用程序。
Restaking 奖项获奖者
此类别鼓励团队在Zircuit生态系统内的AI驱动zkEVM上进行构建,着重于支持AI增强安全性和创新zk rollup技术的项目。
- RestakerX: 一个仪表板应用程序,设计用于跟踪Zircuit网络上的数字资产,提供算法建议以最大化收益。
有关所有项目的更多详细信息和此次黑客马拉松中展示的创新理念的进一步见解,请访问 ETHBratislava Hackathon页面。
关于组织者
Ethereum Bratislava
Ethereum Bratislava 是中欧和东欧地区区块链和技术领域的一个重要社区,致力于推进以太坊的开发和整合。由一支专家团队支持,该组织在增强以太坊在中欧和东欧地区的可扩展性和安全性的项目中作出了重大贡献。积极参与社区活动和教育活动强调了他们在区块链领域促进技术创新和知识共享的承诺。Ethereum Bratislava 继续支持技术改进和生态系统增长,旨在增强以太坊的能力和跨各行业的采用。
-
 @ 04c915da:3dfbecc9
2025-05-16 18:06:46
@ 04c915da:3dfbecc9
2025-05-16 18:06:46Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Using stolen bitcoin for the reserve creates a perverse incentive. If governments see bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 127d3bf5:466f416f
2025-06-01 12:39:00
@ 127d3bf5:466f416f
2025-06-01 12:39:00In the Name of Allah, the Most Gracious, the Most Merciful,
"Permission to fight (against disbelievers) is given to those (believers) who are fought against, because they have been wronged and surely, Allah is Able to give them (believers) victory" [Quran 22:39]
"Those who believe, fight in the Cause of Allah, and those who disbelieve, fight in the cause of Taghut (anything worshipped other than Allah e.g. Satan). So fight you against the friends of Satan; ever feeble is indeed the plot of Satan."[Quran 4:76]
Some American writers have published articles under the title 'On what basis are we fighting?' These articles have generated a number of responses, some of which adhered to the truth and were based on Islamic Law, and others which have not. Here we wanted to outline the truth - as an explanation and warning - hoping for Allah's reward, seeking success and support from Him.
While seeking Allah's help, we form our reply based on two questions directed at the Americans:
(Q1) Why are we fighting and opposing you?\ (Q2) What are we calling you to, and what do we want from you?
As for the first question: Why are we fighting and opposing you? The answer is very simple:
(1) Because you attacked us and continue to attack us.
a) You attacked us in Palestine:
(i) Palestine, which has sunk under military occupation for more than 80 years. The British handed over Palestine, with your help and your support, to the Jews, who have occupied it for more than 50 years; years overflowing with oppression, tyranny, crimes, killing, expulsion, destruction and devastation. The creation and continuation of Israel is one of the greatest crimes, and you are the leaders of its criminals. And of course there is no need to explain and prove the degree of American support for Israel. The creation of Israel is a crime which must be erased. Each and every person whose hands have become polluted in the contribution towards this crime must pay its*price, and pay for it heavily.
(ii) It brings us both laughter and tears to see that you have not yet tired of repeating your fabricated lies that the Jews have a historical right to Palestine, as it was promised to them in the Torah. Anyone who disputes with them on this alleged fact is accused of anti-semitism. This is one of the most fallacious, widely-circulated fabrications in history. The people of Palestine are pure Arabs and original Semites. It is the Muslims who are the inheritors of Moses (peace be upon him) and the inheritors of the real Torah that has not been changed. Muslims believe in all of the Prophets, including Abraham, Moses, Jesus and Muhammad, peace and blessings of Allah be upon them all. If the followers of Moses have been promised a right to Palestine in the Torah, then the Muslims are the most worthy nation of this.
When the Muslims conquered Palestine and drove out the Romans, Palestine and Jerusalem returned to Islaam, the religion of all the Prophets peace be upon them. Therefore, the call to a historical right to Palestine cannot be raised against the Islamic Ummah that believes in all the Prophets of Allah (peace and blessings be upon them) - and we make no distinction between them.
(iii) The blood pouring out of Palestine must be equally revenged. You must know that the Palestinians do not cry alone; their women are not widowed alone; their sons are not orphaned alone.
(b) You attacked us in Somalia; you supported the Russian atrocities against us in Chechnya, the Indian oppression against us in Kashmir, and the Jewish aggression against us in Lebanon.
(c) Under your supervision, consent and orders, the governments of our countries which act as your agents, attack us on a daily basis;
(i) These governments prevent our people from establishing the Islamic Shariah, using violence and lies to do so.
(ii) These governments give us a taste of humiliation, and places us in a large prison of fear and subdual.
(iii) These governments steal our Ummah's wealth and sell them to you at a paltry price.
(iv) These governments have surrendered to the Jews, and handed them most of Palestine, acknowledging the existence of their state over the dismembered limbs of their own people.
(v) The removal of these governments is an obligation upon us, and a necessary step to free the Ummah, to make the Shariah the supreme law and to regain Palestine. And our fight against these governments is not separate from out fight against you.
(d) You steal our wealth and oil at paltry prices because of you international influence and military threats. This theft is indeed the biggest theft ever witnessed by mankind in the history of the world.
(e) Your forces occupy our countries; you spread your military bases throughout them; you corrupt our lands, and you besiege our sanctities, to protect the security of the Jews and to ensure the continuity of your pillage of our treasures.
(f) You have starved the Muslims of Iraq, where children die every day. It is a wonder that more than 1.5 million Iraqi children have died as a result of your sanctions, and you did not show concern. Yet when 3000 of your people died, the entire world rises and has not yet sat down.
(g) You have supported the Jews in their idea that Jerusalem is their eternal capital, and agreed to move your embassy there. With your help and under your protection, the Israelis are planning to destroy the Al-Aqsa mosque. Under the protection of your weapons, Sharon entered the Al-Aqsa mosque, to pollute it as a preparation to capture and destroy it.
(2) These tragedies and calamities are only a few examples of your oppression and aggression against us. It is commanded by our religion and intellect that the oppressed have a right to return the aggression. Do not await anything from us but Jihad, resistance and revenge. Is it in any way rational to expect that after America has attacked us for more than half a century, that we will then leave her to live in security and peace?!!
(3) You may then dispute that all the above does not justify aggression against civilians, for crimes they did not commit and offenses in which they did not partake:
(a) This argument contradicts your continuous repetition that America is the land of freedom, and its leaders in this world. Therefore, the American people are the ones who choose their government by way of their own free will; a choice which stems from their agreement to its policies. Thus the American people have chosen, consented to, and affirmed their support for the Israeli oppression of the Palestinians, the occupation and usurpation of their land, and its continuous killing, torture, punishment and expulsion of the Palestinians. The American people have the ability and choice to refuse the policies of their Government and even to change it if they want.
(b) The American people are the ones who pay the taxes which fund the planes that bomb us in Afghanistan, the tanks that strike and destroy our homes in Palestine, the armies which occupy our lands in the Arabian Gulf, and the fleets which ensure the blockade of Iraq. These tax dollars are given to Israel for it to continue to attack us and penetrate our lands. So the American people are the ones who fund the attacks against us, and they are the ones who oversee the expenditure of these monies in the way they wish, through their elected candidates.
(c) Also the American army is part of the American people. It is this very same people who are shamelessly helping the Jews fight against us.
(d) The American people are the ones who employ both their men and their women in the American Forces which attack us.
(e) This is why the American people cannot be not innocent of all the crimes committed by the Americans and Jews against us.
(f) Allah, the Almighty, legislated the permission and the option to take revenge. Thus, if we are attacked, then we have the right to attack back. Whoever has destroyed our villages and towns, then we have the right to destroy their villages and towns. Whoever has stolen our wealth, then we have the right to destroy their economy. And whoever has killed our civilians, then we have the right to kill theirs.
The American Government and press still refuses to answer the question:
Why did they attack us in New York and Washington?
If Sharon is a man of peace in the eyes of Bush, then we are also men of peace!!! America does not understand the language of manners and principles, so we are addressing it using the language it understands.
(Q2) As for the second question that we want to answer: What are we calling you to, and what do we want from you?
(1) The first thing that we are calling you to is Islam.
(a) The religion of the Unification of God; of freedom from associating partners with Him, and rejection of this; of complete love of Him, the Exalted; of complete submission to His Laws; and of the discarding of all the opinions, orders, theories and religions which contradict with the religion He sent down to His Prophet Muhammad (peace be upon him). Islam is the religion of all the prophets, and makes no distinction between them - peace be upon them all.
It is to this religion that we call you; the seal of all the previous religions. It is the religion of Unification of God, sincerity, the best of manners, righteousness, mercy, honour, purity, and piety. It is the religion of showing kindness to others, establishing justice between them, granting them their rights, and defending the oppressed and the persecuted. It is the religion of enjoining the good and forbidding the evil with the hand, tongue and heart. It is the religion of Jihad in the way of Allah so that Allah's Word and religion reign Supreme. And it is the religion of unity and agreement on the obedience to Allah, and total equality between all people, without regarding their colour, sex, or language.
(b) It is the religion whose book - the Quran - will remained preserved and unchanged, after the other Divine books and messages have been changed. The Quran is the miracle until the Day of Judgment. Allah has challenged anyone to bring a book like the Quran or even ten verses like it.
(2) The second thing we call you to, is to stop your oppression, lies, immorality and debauchery that has spread among you.
(a) We call you to be a people of manners, principles, honour, and purity; to reject the immoral acts of fornication, homosexuality, intoxicants, gambling's, and trading with interest.
We call you to all of this that you may be freed from that which you have become caught up in; that you may be freed from the deceptive lies that you are a great nation, that your leaders spread amongst you to conceal from you the despicable state to which you have reached.
(b) It is saddening to tell you that you are the worst civilization witnessed by the history of mankind:
(i) You are the nation who, rather than ruling by the Shariah of Allah in its Constitution and Laws, choose to invent your own laws as you will and desire. You separate religion from your policies, contradicting the pure nature which affirms Absolute Authority to the Lord and your Creator. You flee from the embarrassing question posed to you: How is it possible for Allah the Almighty to create His creation, grant them power over all the creatures and land, grant them all the amenities of life, and then deny them that which they are most in need of: knowledge of the laws which govern their lives?
(ii) You are the nation that permits Usury, which has been forbidden by all the religions. Yet you build your economy and investments on Usury. As a result of this, in all its different forms and guises, the Jews have taken control of your economy, through which they have then taken control of your media, and now control all aspects of your life making you their servants and achieving their aims at your expense; precisely what Benjamin Franklin warned you against.
(iii) You are a nation that permits the production, trading and usage of intoxicants. You also permit drugs, and only forbid the trade of them, even though your nation is the largest consumer of them.
(iv) You are a nation that permits acts of immorality, and you consider them to be pillars of personal freedom. You have continued to sink down this abyss from level to level until incest has spread amongst you, in the face of which neither your sense of honour nor your laws object.
Who can forget your President Clinton's immoral acts committed in the official Oval office? After that you did not even bring him to account, other than that he 'made a mistake', after which everything passed with no punishment. Is there a worse kind of event for which your name will go down in history and remembered by nations?
(v) You are a nation that permits gambling in its all forms. The companies practice this as well, resulting in the investments becoming active and the criminals becoming rich.
(vi) You are a nation that exploits women like consumer products or advertising tools calling upon customers to purchase them. You use women to serve passengers, visitors, and strangers to increase your profit margins. You then rant that you support the liberation of women.
(vii) You are a nation that practices the trade of sex in all its forms, directly and indirectly. Giant corporations and establishments are established on this, under the name of art, entertainment, tourism and freedom, and other deceptive names you attribute to it.
(viii) And because of all this, you have been described in history as a nation that spreads diseases that were unknown to man in the past. Go ahead and boast to the nations of man, that you brought them AIDS as a Satanic American Invention.
(xi) You have destroyed nature with your industrial waste and gases more than any other nation in history. Despite this, you refuse to sign the Kyoto agreement so that you can secure the profit of your greedy companies and*industries.
(x) Your law is the law of the rich and wealthy people, who hold sway in their political parties, and fund their election campaigns with their gifts. Behind them stand the Jews, who control your policies, media and economy.
(xi) That which you are singled out for in the history of mankind, is that you have used your force to destroy mankind more than any other nation in history; not to defend principles and values, but to hasten to secure your interests and profits. You who dropped a nuclear bomb on Japan, even though Japan was ready to negotiate an end to the war. How many acts of oppression, tyranny and injustice have you carried out, O callers to freedom?
(xii) Let us not forget one of your major characteristics: your duality in both manners and values; your hypocrisy in manners and principles. All*manners, principles and values have two scales: one for you and one for the others.
(a)The freedom and democracy that you call to is for yourselves and for white race only; as for the rest of the world, you impose upon them your monstrous, destructive policies and Governments, which you call the 'American friends'. Yet you prevent them from establishing democracies. When the Islamic party in Algeria wanted to practice democracy and they won the election, you unleashed your agents in the Algerian army onto them, and to attack them with tanks and guns, to imprison them and torture them - a new lesson from the 'American book of democracy'!!!
(b)Your policy on prohibiting and forcibly removing weapons of mass destruction to ensure world peace: it only applies to those countries which you do not permit to possess such weapons. As for the countries you consent to, such as Israel, then they are allowed to keep and use such weapons to defend their security. Anyone else who you suspect might be manufacturing or keeping these kinds of weapons, you call them criminals and you take military action against them.
(c)You are the last ones to respect the resolutions and policies of International Law, yet you claim to want to selectively punish anyone else who does the same. Israel has for more than 50 years been pushing UN resolutions and rules against the wall with the full support of America.
(d)As for the war criminals which you censure and form criminal courts for - you shamelessly ask that your own are granted immunity!! However, history will not forget the war crimes that you committed against the Muslims and the rest of the world; those you have killed in Japan, Afghanistan, Somalia, Lebanon and Iraq will remain a shame that you will never be able to escape. It will suffice to remind you of your latest war crimes in Afghanistan, in which densely populated innocent civilian villages were destroyed, bombs were dropped on mosques causing the roof of the mosque to come crashing down on the heads of the Muslims praying inside. You are the ones who broke the agreement with the Mujahideen when they left Qunduz, bombing them in Jangi fort, and killing more than 1,000 of your prisoners through suffocation and thirst. Allah alone knows how many people have died by torture at the hands of you and your agents. Your planes remain in the Afghan skies, looking for anyone remotely suspicious.
(e)You have claimed to be the vanguards of Human Rights, and your Ministry of Foreign affairs issues annual reports containing statistics of those countries that violate any Human Rights. However, all these things vanished when the Mujahideen hit you, and you then implemented the methods of the same documented governments that you used to curse. In America, you captured thousands the Muslims and Arabs, took them into custody with neither reason, court trial, nor even disclosing their names. You issued newer, harsher laws.
What happens in Guatanamo is a historical embarrassment to America and its values, and it screams into your faces - you hypocrites, "What is the value of your signature on any agreement or treaty?"
(3) What we call you to thirdly is to take an honest stance with yourselves - and I doubt you will do so - to discover that you are a nation without principles or manners, and that the values and principles to you are something which you merely demand from others, not that which you yourself must adhere to.
(4) We also advise you to stop supporting Israel, and to end your support of the Indians in Kashmir, the Russians against the Chechens and to also cease supporting the Manila Government against the Muslims in Southern Philippines.
(5) We also advise you to pack your luggage and get out of our lands. We desire for your goodness, guidance, and righteousness, so do not force us to send you back as cargo in coffins.
(6) Sixthly, we call upon you to end your support of the corrupt leaders in our countries. Do not interfere in our politics and method of education. Leave us alone, or else expect us in New York and Washington.
(7) We also call you to deal with us and interact with us on the basis of mutual interests and benefits, rather than the policies of sub dual, theft and occupation, and not to continue your policy of supporting the Jews because this will result in more disasters for you.
If you fail to respond to all these conditions, then prepare for fight with the Islamic Nation. The Nation of Monotheism, that puts complete trust on Allah and fears none other than Him. The Nation which is addressed by its Quran with the words: "Do you fear them? Allah has more right that you should fear Him if you are believers. Fight against them so that Allah will punish them by your hands and disgrace them and give you victory over them and heal the breasts of believing people. And remove the anger of their (believers') hearts. Allah accepts the repentance of whom He wills. Allah is All-Knowing, All-Wise." [Quran9:13-1]
The Nation of honour and respect:
"But honour, power and glory belong to Allah, and to His Messenger (Muhammad- peace be upon him) and to the believers." [Quran 63:8]
"So do not become weak (against your enemy), nor be sad, and you will be*superior ( in victory )if you are indeed (true) believers" [Quran 3:139]
The Nation of Martyrdom; the Nation that desires death more than you desire life:
"Think not of those who are killed in the way of Allah as dead. Nay, they are alive with their Lord, and they are being provided for. They rejoice in what Allah has bestowed upon them from His bounty and rejoice for the sake of those who have not yet joined them, but are left behind (not yet martyred) that on them no fear shall come, nor shall they grieve. They rejoice in a grace and a bounty from Allah, and that Allah will not waste the reward of the believers." [Quran 3:169-171]
The Nation of victory and success that Allah has promised:
"It is He Who has sent His Messenger (Muhammad peace be upon him) with guidance and the religion of truth (Islam), to make it victorious over all other religions even though the Polytheists hate it." [Quran 61:9]
"Allah has decreed that 'Verily it is I and My Messengers who shall be victorious.' Verily Allah is All-Powerful, All-Mighty." [Quran 58:21]
The Islamic Nation that was able to dismiss and destroy the previous evil Empires like yourself; the Nation that rejects your attacks, wishes to remove your evils, and is prepared to fight you. You are well aware that the Islamic Nation, from the very core of its soul, despises your haughtiness and arrogance.
If the Americans refuse to listen to our advice and the goodness, guidance and righteousness that we call them to, then be aware that you will lose this Crusade Bush began, just like the other previous Crusades in which you were humiliated by the hands of the Mujahideen, fleeing to your home in great silence and disgrace. If the Americans do not respond, then their fate will be that of the Soviets who fled from Afghanistan to deal with their military defeat, political breakup, ideological downfall, and economic bankruptcy.
This is our message to the Americans, as an answer to theirs. Do they now know why we fight them and over which form of ignorance, by the permission of Allah, we shall be victorious?
-
 @ 84b0c46a:417782f5
2025-05-31 09:11:23
@ 84b0c46a:417782f5
2025-05-31 09:11:23Simple Long Form Content Editor (NIP-23)
機能
-
nostr:npub1sjcvg64knxkrt6ev52rywzu9uzqakgy8ehhk8yezxmpewsthst6sw3jqcw や、 nostr:nevent1qvzqqqqqqypzq4jsz7zew5j7jr4pdfxh483nwq9vyw9ph6wm706sjwrzj2we58nqqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyxhwumn8ghj7mn0wvhxcmmvqqsgcn99jyn5tevxz5zxsrkd7h0sx8fwnqztula423xh83j9wau7cms3vg9c7 のようにnostr:要素を挿入できる (メニューのNアイコンから挿入またはnostr:note~~のように手動で入力)
-
:monoice:のようにカスタム絵文字を挿入できる(メニューの🙂アイコンから)
:monopaca_kao:
:kubipaca_karada:
- 新規記事作成と、既存記事の修正ができる
やることやったこと
-
[x] nostr:を投稿するときにtagにいれる
-
[x] 画像をアップロードできるようにする(NIP-96)
 できる
できる - [x] 投稿しましたログとかをトースト的なやつでだすようにする
- [ ] レイアウトを整える
- [ ] あとなんか
test
nostr:naddr1qvzqqqr4gupzpp9sc34tdxdvxh4jeg5xgu9ctcypmvsg0n00vwfjydkrjaqh0qh4qqxnzde58q6njvpkxqersv3ejxw9x9
-
-
 @ e2c72a5a:bfacb2ee
2025-06-05 17:00:01
@ e2c72a5a:bfacb2ee
2025-06-05 17:00:01Forget Lambos, think real estate tokens.
A European fund just dropped $3.4 million on tokenized real estate, marking the first time big money directly bought retail available tokens. This isn't just about crypto hype; it's about institutions embracing regulated crypto assets. Real World Assets (RWAs) are booming, up 260% this year, fueled by clearer US crypto rules. This surge pushes the tokenization sector past $23 billion.
Is this the start of crypto's mainstream moment?
-
 @ fbf0e434:e1be6a39
2025-06-05 14:06:35
@ fbf0e434:e1be6a39
2025-06-05 14:06:35Hackathon 概要
Verifiable AI Hackathon 由 cheqd 主办,聚焦通过安全、可验证的道德系统构建可信 AI 生态。活动吸引 278 名开发者参与,共提交 21 个项目,致力于推动可信 AI 环境的建立。开发者针对 AI 技术滥用问题(如 deepfake 欺诈)及透明化、道德化 AI 系统构建挑战提出解决方案。
参与者围绕自主经济、AI 验证、安全数据应用等主题,借助 cheqd 的去中心化标识符(DID)与可验证凭证(VC)技术展开探索。核心成果包括内容认证创新方案,以及通过验证数据集防范虚假信息的应用实践。
本次黑客松凸显了 AI 解决方案需以透明度和用户权益为核心的发展方向,旨在通过区块链工具为开发者赋能,夯实安全可靠的 AI 应用基础。这一举措致力于将数字身份与 AI 的交互模式,升级为兼顾可持续性与隐私保护的新型范式。
Hackathon 获奖者
AI Agents 奖项获奖者
- Kith: 这个去中心化系统利用加密的可验证凭证,通过去中心化标识符(DIDs)确保 AI 代理的隐私、认证和可信度。
- Identone: 该项目通过在电话交谈中验证身份来保障人与AI语音代理之间的互动可信度。
- SNAILS.: 利用去中心化数字身份来验证内容的机器人,从而增强 AI 环境中的信任。
其他奖项获奖者
- CheqDeep: 利用区块链技术认证媒体内容,通过 DID 链接资源验证人类来源和真实性。
- Trusty Bytes: 为 AI 代理提供一个获取经过验证数据的市场,使用基于区块链的验证来确保可信交易。
- crdbl: 一个平台,通过可验证凭证、去中心化身份、加密签名和AI验证来提升在线可信度。
构建一个整合私人用户数据的Agent奖项获奖者
- Viskify: 一个AI辅助手的平台,用于人才验证,利用可验证凭证和确定性去中心化标识符,并与 Stripe 和 Verida 集成以进行账单和私人数据管理。
有关所有项目的更多信息,请访问 The Verifiable AI Hackathon。
关于主办方
cheqd
cheqd 是区块链行业的重要参与者,专注于数字身份解决方案。该组织以其在建立支持安全和注重隐私数据管理的去中心化身份基础设施中所扮演的角色而闻名。通过利用最前沿的区块链技术,cheqd 在身份生态系统的标准开发中发挥了关键作用。其努力包括建立战略合作伙伴关系,以创建可互操作的身份服务。秉承加强数字信任框架的承诺,cheqd 继续通过先进且有效的身份管理解决方案来赋能个人和组织。
-
 @ 1c5ff3ca:efe9c0f6
2025-06-05 06:29:45
@ 1c5ff3ca:efe9c0f6
2025-06-05 06:29:45Just calling it Open is not enough - Herausforderungen öffentlicher Bildungsinfrastrukturen und wie Nostr helfen könnte
Ich möchte gerne mit euch teilen, an welchen Konzepten ich arbeite, um die öffentliche Bildungsinfrastruktur mit Hilfe von Nostr zugänglicher und offener zu gestalten. Ich arbeite im Bereich öffentlicher Bildungsinfrastrukturen, besonders im Feld von Open Educational Resources (#OER). OER sind offen lizenzierte Bildungsmaterialien, die mit einer offenen Lizenz, meist einer Creative Commons Lizenz, versehen sind (CC-0, CC-BY, CC-BY-SA). Durch die klare und offene Lizenzierung ist es leicht möglich, die Lernmaterialien auf die individuellen Bedarfe anzupassen, sie zu verbessern und sie erneut zu veröffentlichen.
Seit vielen Jahren wird einerseits die Entwicklung freier Bildungsmaterialien gefördert, andererseits werden Plattformen, insbesondere Repositorien gefördert, die diese Materialien verfügbar machen sollen. Denn irgendwo müssen diese Materialien zur Verfügung gestellt werden, damit sie auch gefunden werden können.
Das klappt allerdings nur so mittelgut.
Herausforderungen
Nach vielen Jahren Förderung kann die einfache Frage: "Wo kann ich denn mein OER-Material bereitstellen" nicht einfach beantwortet werden. Es gibt Services, bei denen ich mein OER hochladen kann, jedoch bleibt es dann eingeschlossen in dieser Plattform und wird nicht auf anderen Plattformen auffindbar. Außerdem sind diese Services häufig an bestimmte Bildungskontexte gebunden oder geben Content erst nach einer Qualitätsprüfung frei. Dies führt dazu, dass ein einfaches und gleichzeitig öffentliches Teilen nicht möglich ist.
Diese und weitere Herausforderungen haben ihren Ursprung darin, dass Service und Infrastruktur in der Architektur öffentlichen Bildungsarchitektur ungünstig vermischt werden. Als Infrastruktur verstehe ich hier die Bereitstellung einer öffentlichen und offen zugänglichen Bildungsinfrastruktur, auf der Daten ausgetauscht, also bereitgestellt und konsumiert werden können. Jedoch existiert eine solche Infrstruktur momentan nicht unabhängig von den Services, die auf ihr betrieben werden. Infrastrukturbetreiber sind momentan gleichzeitig immer Servicebetreiber. Da sie aber die Hand darüber haben wollen, was genau in ihrem Service passiert (verständlich), schränken sie den Zugang zu ihrer Infrastruktur mit ein, was dazu führt, dass sie Lock-In Mechanismen großer Medienplattformen in der kleinen öffentlichen Bildungsinfrastruktur replizieren.
Es ist in etwas so, als würde jeder Autobauer auch gleichzeitig die Straßen für seine Fahrzeuge bauen. Aber halt nur für seine Autos.
Anhand einiger beispielhafter Services, die bestehende Plattformen auf ihren Infrastrukturen anbieten, möchte ich die Herausforderungen aufzeigen, die ich im aktuellen Architekturkonzept sehe:
- Upload von Bildungsmaterial
- Kuration: Zusammenstellung von Listen, Annotation mit Metadaten
- Crawling, Indexierung und Suche
- Plattfformübergreifende Kollaboration in Communities -> Beispiel: Qualitätssicherung (was auch immer das genau bedeutet)
- KI- Services -> Beispiel: KI generierte Metadaten für BiIdungsmaterial
Material Upload
Der Service "Material-Upload" oder das Mitteilen eines Links zu einem Bildungsmaterial wird von verschiedenen OER-Pattformen bereitgestellt (wirlernenonline.de, oersi.org, mundo.schule).
Dies bedeutet konkret: Wenn ich bei einer der Plattformen Content hochlade, verbleibt der Content in der Regel auch dort und wird nicht mit den anderen Plattformen geteilt. Das Resultat für die User: Entweder muss ich mich überall anmelden und dort mein Material hochladen (führt zu Duplikaten) oder damit leben, dass eben nur die Nutzer:innen der jeweiligen Plattform meinen Content finden können.
Der "Open Educational Resource Search Index" (OERSI) geht diese Herausforderung an, indem die Metadaten zu den Bildungsmaterialien verschiedener Plattformen in einem Index bereitgestellt werden. Dieser Index ist wiederum öffentlich zugänglich, sodass Plattformen darüber auch Metadaten anderer Plattformen konsumieren können. Das ist schon sehr gut. Jedoch funktioniert das nur für Plattformen, die der OERSI indexiert und für alle anderen nicht. Der OERSI ist auf den Hochschulbereich fokussiert, d.h. andere Bildungskontexte werden hier ausgeschlossen. Der Ansatz für jeden Bildungsbereich einen passenden "OERSI" daneben zustellen skaliert und schlecht und es bleibt die Herausforderung bestehen, dass für jede Quelle, die indexiert werden soll, ein entsprechender Importer/Crawler geschrieben werden muss.
Dieser Ansatz (Pull-Ansatz) rennt den Materialien hinterher.
Es gibt jedoch noch mehr Einschränkungen: Die Plattformen haben sich jeweils auf spezifische Bildungskontexte spezialisiert. D.h. auf die Fragen: Wo kann ich denn mein OER bereitstellen, muss immer erst die Gegenfrage: "Für welchen Bildungsbereich denn?" beantwortet werden. Wenn dieser außerhalb des allgemeinbildendenden Bereichs oder außerhalb der Hochschule liegt, geschweige denn außerhalb des institutionellen Bildungsrahmens, wird es schon sehr, sehr dünn. Kurzum:
- Es ist nicht einfach möglich OER bereitzustellen, sodass es auch auf verschiedenen Plattformen gefunden werden kann.
Kuration
Unter Kuration verstehe ich hier die Zusammenstellung von Content in Listen oder Sammlungs ähnlicher Form sowie die Annotation dieser Sammlungen oder des Contents mit Metadaten.
Einige Plattformen bieten die Möglichkeit an, Content in Listen einzuordnen. Diese Listen sind jedoch nicht portabel. Die Liste, die ich auf Plattform A erstelle, lässt sich nicht auf Plattform B importieren. Das wäre aber schön, denn so könnten die Listen leichter auf anderen Plattformen erweitert oder sogar kollaborativ gestaltet werden, andererseits werden Lock-In-Effekte zu vermieden.
Bei der Annotation mit Metadaten treten verschiedene zentralisierende Faktoren auf. In der momentanen Praxis werden die Metadaten meist zum Zeitpunkt der Contentbereitstellung festgelegt. Meist durch eine Person oder Redaktion, bisweilen mit Unterstützung von KI-Services, die bei der Metadateneingabe unterstützen. Wie aber zusätzliche eigene Metadaten ergänzen? Wie mitteilen, dass dieses Material nicht nur für Biologie, sondern auch für Sport in Thema XY super einsetzbar wäre? Die momentanen Ansätze können diese Anforderung nicht erfüllen. Sie nutzen die Kompetenz und das Potential ihrer User nicht.
- Es gibt keine interoperablen Sammlungen
- Metadaten-Annotation ist zentralisiert
- User können keine eigenen Metadaten hinzufügen
Crawling, Indexierung und Suche

Da die Nutzer:innen nicht viele verschiedene Plattformen und Webseiten besuchen wollen, um dort nach passendem Content zu suchen, crawlen die "großen" OER-Aggregatoren diese, um die Metadaten des Contents zu indexieren. Über verschiedene Schnittstellen oder gerne auch mal über das rohe HTML. Letztere Crawler sind sehr aufwändig zu schreiben, fehleranfällig und gehen bei Design-Anpassungen der Webseite schnell kaputt, erstere sind etwas stabiler, solange sich die Schnittstelle nicht ändert. Durch den Einsatz des Allgemeinen Metadatenprofils für Bildungsressourcen (AMB) hat sich die Situation etwas verbessert. Einige Plattformen bieten jetzt eine Sitemap an, die Links zu Bildungsmaterial enthalten, die wiederum eingebettet
script-tags vom Typapplication/ld+jsonenthalten, sodass die Metadaten von dort importiert werden können.Beispiel: e-teaching.org bietet hier eine Sitemap für ihre OER an: https://e-teaching.org/oer-sitemap.xml und auf den jeweiligen Seiten findet sich ein entsprechendes script-Tag.
Das ist schon viel besser, aber da geht noch mehr:
Zunächst ist dieser Ansatz nur für Plattformen und Akteure praktikabel, die über IT-Ressourcen verfügen, um entsprechende Funktionalitäten bei sich einbauen zu können. Lehrende können dies nicht einfach auf ihrem privaten Blog oder ähnliches umsetzen. Zum anderen besteht immer noch ein Discovery Problem. Ich muss nach wie vor wissen, wo ich suchen muss. Ich muss die Sitemaps kennen, sonst finde ich nichts. Statt eines Ansatzes, bei dem Akteure eigenständig mitteilen können, dass sie neuen Content haben (Push-Ansatz), verfolgen wir derzeit einen Ansatz, bei dem jede Plattform für sich Content im Pull-Verfahren akquiriert. Dies führt an vielen Stellen zu Doppelarbeiten, ist ineffizient (mehrere Personen bauen genau die gleichen Crawler, aber halt immer für ihre Plattform) und schliesst vor allem kleine Akteure aus (lohnt es sich einen Crawler zu programmieren, wenn die Webseite "nur" 50 Materialien bereitstellt?).
Anstatt erschlossene Daten zu teilen, arbeiten die Plattformen für sich oder stellen es höchstens wieder hinter eigenen (offenen oder geschlossenen) Schnittstellen bereit. Das ist wohl nicht das, was wir uns unter einer offenen und kollaborativen Gemeinschaft vorstellen, oder?
Bei der Suche stehen wir vor ähnlichen Herausforderungen, wie bereits oben geschildert. Obwohl verschiedene OER-Aggregatoren in Form von Repositorien oder Referatorien bereits viele der "kleineren" Plattformen indexieren und somit eine übergreifende Suche anbieten, ist es nicht möglich, diese Aggregatoren gemeinsam zu durchsuchen. Dies führt im Endeffekt dazu, dass die User wieder verschiedene Plattformen ansteuern müssen, wenn sie den gesamten OER-Fundus durchsuchen wollen.
- An vielen Stellen wird Content doppelt erschlossen, aber immer für die eigene Plattform
- Es gibt keinen geteilten Datenraum, in den Akteure Content "pushen" können
- Es gibt keine plattformübergreifenden Suchmöglichkeiten
Plattformübergreifende Kollaboration
Das wäre schön, oder? Mir ist schleierhaft, wie #OEP (Open Educational Practices, genaue Definition durch die Community steht noch aus) ohne funktionieren soll. Aber es gibt meines Wissens nach nicht mal Ansätze, wie das technisch umgesetzt werden soll (oder doch? let me hear).
Ein Szenario für solche plattformübergreifende Kollaboration könnte Qualitätssicherung sein. Gesetzt, dass sich zwei Plattformen / Communities auf etwas verständigt haben, dass sie als "Qualität" bezeichnen, wie aber dieses Gütesiegel nun an den Content bringen?
Plattform A: Na, dann kommt doch alle zu uns. Hier können wir das machen und dann hängt auch ein schönes Badge an den Materialien.
Plattform B: Ja, aber dann hängt es ja nicht an unseren Materialien. Außerdem wollen/müssen wir bei uns arbeiten, weil welche Existenzberechtigung hat denn meine Plattform noch, wenn wir alles bei dir machen?
- Obwohl nun #OEP in aller Munde sind, gibt es keine technischen Ansätze, wie (plattformübergreifende) Kollaboration technisch abgebildet werden kann
KI-Services
Was ist heute schon komplett ohne das Thema KI zu erwähnen? Mindestens für den nächsten Förderantrag muss auch irgendetwas mit KI gemacht werden...
Verschiedene Projekte erarbeiten hilfreiche und beeindruckende KI-Services. Beispielsweise, um die Annotation von Content mit Metadaten zu erleichtern, Metadaten automatisch hinzuzufügen, Content zu bestimmten Themen zu finden oder (halb-)automatisch zu Sammlungen hinzuzufügen. Aber (vielleicht habt ihr es schon erraten): Funktioniert halt nur auf der eigenen Plattform. Vermutlich, weil die Services nah am plattformeigenen Datenmodell entwickelt werden. Und da die Daten dieses Silo nicht verlassen, passt das schon. Das führt dazu, dass an mehreren Stellen die gleichen Services doppelt entwickelt werden.
- KI-Services funktionieren oft nur auf der Plattform für die sie entwickelt werden
Zusammenfassung der Probleme
Wir machen übrigens vieles schon sehr gut (Einsatz des AMB, Offene Bidungsmaterialien, wir haben eine großartige Community) und jetzt müssen wir halt weiter gehen.
(Die OER-Metadatengruppe, die das Allgemeine Metadatenprofil für Bildungsressourcen (AMB) entwickelt hat, bekommt für ihre Arbeit keine direkte Förderung. Gleichzeitig ist sie eine zentrale Anlaufstelle für alle, die mit Metadaten in offenen Bildungsinfrastukturen hantieren und das Metadatenprofil ist eines der wenigen Applikationsprofile, das öffentlich einsehbar, gut dokumentiert ist und Validierungsmöglichkeiten bietet.)
Betrachten wir die gesamten Plattformen und die beschriebenen Herausforderungen aus der Vogelperspektive, so lassen sich drei ineinander verschränkte Kernbestandteile unterscheiden, die helfen, die beschriebenen Probleme besser zu verstehen:
- User
- Service
- Daten
User: Auf (fast) allen Plattformen agieren User. Sie laden Material hoch, annotieren mit Metadaten, sind in einer Community, suchen Content usw. Egal, ob sie sich einloggen können/müssen, irgendetwas bieten wir unseren Usern an, damit sie daraus hoffentlich Mehrwerte ziehen
Service: Das ist dieses irgendetwas. Die "Webseite", die Oberfläche, das, wo der User klicken und etwas tun kann. Es ist das, was den Daten oft eine "visuelle" Form gibt. Der Service ist der Mittler, das Interface zwischen User und Daten. Mithilfe des Services lassen sich Daten erzeugen, verändern oder entfernen (Es gibt natürlich auch viele nicht-visuelle Services, die Interaktion mit Daten ermöglichen, aber für die meisten normalen Menschen, gibt es irgendwo was zu klicken).
Daten: Die Informationen in strukturierter maschinenlesbarer Form, die dem User in gerenderter Form durch einen Service Mehrwerte bieten können. Ungerenderte Daten können wir schwieirg erfassen (wir sind ja nicht Neo). Das können entweder die Metadaten zu Bildungmaterialien sein, die Materialien selbst, Profilinformationen, Materialsammlungen o.ä.

Meines Erachtens nach haben viele der oben beschriebenen Herausforderungen ihren Ursprung darin, dass die drei Kernbestandteile User, Service, Daten ungünstig miteinander verbunden wurden. Was kein Vorwurf sein soll, denn das ist genau die Art und Weise, wie die letzten Jahre (Jahrzehnte?) Plattformen immer gebaut wurden:
- User, Service und Daten werden in einer Plattform gebündelt
Das heisst durch meinen Service agieren die User mit den Daten und ich kann sicherstellen, dass in meiner kleinen Welt alles gut miteinander funktioniert. Sinnvoll, wenn ich Microsoft, Facebook, X oder ähnliches bin, weil mein Geschäftsmodell genau darin liegt: User einschließen (lock-in), ihnen die Hohheit über ihren Content nehmen (oder kannst du deine Facebook Posts zu X migrieren?) und nach Möglichkeit nicht wieder rauslassen.
Aber unsere Projekte sind öffentlich. Das sind nicht die Mechanismen, die wir replizieren sollten. Also was nun?
Bildungsinfrasstrukturen auf Basis des Nostr-Protokolls
Nostr
Eine pseudonyme Person mit dem Namen "fiatjaf" hat 2019 ein Konzept für ein Social Media Protokoll "Nostr - Notes and Other Stuff Transmitted By Relays" wie folgt beschrieben:
It does not rely on any trusted central server, hence it is resilient, it is based on cryptographic keys and signatures, so it is tamperproof, it does not rely on P2P techniques, therefore it works.
Fiatjaf, 2019
Die Kernbestandsteile des Protokolls bestehen aus:
- JSON -> Datenformat
- SHA256 & Schnorr -> Kryptographie
- Websocket -> Datenaustausch
Und funktionieren tut es so:
User besitzen ein "Schlüsselpaar": einen privaten Schlüssel (den behälst du für dich, nur für dich) und einen öffentlichen Schlüssel, den kannst du herumzeigen, das ist deine öffentliche Identität. Damit sagst du anderen Usern: Hier schau mal, das bin ich. Die beiden Schlüssel hängen dabei auf eine "magische" (kryptografische) Weise zusammen: Der öffentliche Schlüssel lässt sich aus dem privaten Schlüssel generieren, jedoch nicht andersherum. D.h. falls du deinen öffentlichen Schlüssel verlierst: Kein Problem, der lässt sich immer wieder herstellen. Wenn du deinen privaten Schlüssel verlierst: Pech gehabt, es ist faktisch unmöglich, diesen wieder herzustellen.
Die Schlüsselmagie geht jedoch noch weiter: Du kannst mit deinem privaten Schlüssel "Nachrichten" signieren, also wie unterschreiben. Diese Unterschrift, die du mit Hilfe des privaten Schlüssels erstellst, hat eine magische Eigenschaft: Jeder kann mithilfe der Signatur und deinem öffentlichen* Schlüssel nachprüfen, dass nur die Person, die auch den privaten Schlüssel zu diesem öffentlichen Schlüssel besitzt, diese Nachricht unterschrieben haben kann. Magisch, richtig? Verstehst du nicht komplett? Nicht schlimm, du benutzt es bereits vermutlich, ohne dass du es merkst. Das ist keine fancy neue Technologie, sondern gut abgehangen und breit im Einsatz.
Merke: User besitzen ein Schlüsselpaar und können damit Nachrichten signieren.
Dann gibt es noch die Services. Services funktionieren im Grunde wie bereits oben beschrieben. Durch sie interagieren die User mit Daten. Aber bei Nostr ist es ein kleines bisschen anders als sonst, denn: Die Daten "leben" nicht in den Services. Aber wo dann?
Wenn ein User einen Datensatz erstellt, verändert oder entfernen möchte, wird dieses "Event" (so nennen wir das bei Nostr) mit deinem privaten Schlüssel signiert (damit ist für alle klar, nur du kannst das gemacht haben) und dann mehrere "Relays" gesendet. Das sind die Orte, wo die Daten gehalten werden. Wenn ein User sich in einen Service einloggt, dann holt sich der Service die Daten, die er braucht von diesen Relays. User, Service und Daten sind also entkoppelt. Der User könnte zu einem anderen Service wechseln und sich dieseleben Daten von den Relays holen. Keine Lock-In Möglichkeiten.
Merke: User, Service und Daten sind entkoppelt.
Zuletzt gibt es noch die Relays. Relays sind Orte. Es sind die Orte, zu denen die Events, also die Daten der User, ihre Interaktionen, gesendet und von denen sie angefragt werden. Sie sind sowas wie das Backend von Nostr, allerdings tun sie nicht viel mehr als das: Events annehmen, Events verteilen. Je nach Konfiguration dürfen nur bestimmte User auf ein Relay schreiben oder davon lesen.
Das Protokoll ist von seinem Grunddesign auf Offenheit und Interoperabilität ausgelegt. Keine Registrierung ist nötig, sondern nur Schlüsselpaare. Durch kryptografische Verfahren kann dennoch die Authentizitität eines Events sichergestellt werden, da nur die Inhaberin des jeweiligen Schlüsselpaares dieses Event so erstellen konnte. Die Relays sorgen dafür die Daten an die gewünschten Stellen zu bringen und da wir mehr als nur eines benutzen, haben wir eine gewisse Ausfallsicherheit. Da die Daten nur aus signierten JSON-Schnipseln bestehen, können wir sie leicht an einen anderen Ort kopieren, im Falle eines Ausfalls. Durch die Signaturen ist wiederum sichergestellt, dass zwischendurch keine Veränderungen an den Daten vorgenommen wurden.
Beispiel: Ein Nostr Event
Hier ein kleiner technischer Exkurs, der beschreibt, wie Nostr Events strukturiert sind. Falls dich die technischen Details nicht so interessieren, überspringe diesen Abschnitt ruhig.
Jedes Nostr Event besitzt die gleiche Grundstruktur mit den Attributen:
id: Der Hash des Eventspubkey: Der Pubkey des Urhebers des Eventscreated_at: Der Zeitstempel des Eventskind: Der Typ des Eventstags: Zusätzliche Metadaten für das Event können in diesem Array hinterlegt werdencontent: Der textuelle Inhalt eines Eventssig: Die Signatur des Events, um die Integrität der Daten zu überprüfen
json { "id": <32-bytes lowercase hex-encoded sha256 of the serialized event data>, "pubkey": <32-bytes lowercase hex-encoded public key of the event creator>, "created_at": <unix timestamp in seconds>, "kind": <integer between 0 and 65535>, "tags": [ [<arbitrary string>...], // ... ], "content": <arbitrary string>, "sig": <64-bytes lowercase hex of the signature of the sha256 hash of the serialized event data, which is the same as the "id" field> }Die verwendeten Eventtypen sowie die existierenden Spezifikationen lassen sich unter https://github.com/nostr-protocol/nips/ einsehen.
Wichtig ist auch: Du kannst einfach anfangen, Anwendungen zu entwickeln. Die Relays werden alle Events akzeptieren, die dem o.g. Schema folgen. Du musst also niemanden um Erlaubnis fragen oder warten, bis deine Spezifikation akzeptiert und hinzugefügt wurde.
You can just build things.
Exkurs: Nostr für Binärdaten - Blossom
Ja, aber... das ist doch nur für textbasierte Daten geeignet? Was ist denn mit den Binärdaten (Bilder, Videos, PDFs, etc)
Diese Daten sind oft recht groß und es wurde sich auf das Best-Practice geeignet, diese Daten nicht auf Relays abzulegen, sondern einen besser geeigneten Publikationsmechanismus für diese Datentypen zu finden. Der Ansatz wird als "Blossom - Blobs stored simply on mediaservers" bezeichnet und ist recht unkompliziert.
Blossom Server (nichts anderes als simple Medienserver) nutzen Nostr Schlüsselpaare zur Verwaltung Identitäten und zum Signieren von Events. Die Blobs werden über ihren sha256 Hash identifiziert. Blossom definiert einige standardisierte Endpunkte, die beschreiben wie Medien hochgeladen werden können, wie sie konsumiert werden können usw.
Die Details, wie Authorisierung und die jeweiligen Endpunkte funktionieren, werden in der genannten Spezifikation beschrieben.
Nostr 🤝 Öffentliche Bildungsinfrastrukturen
Wie könnten Herausforderungen gelöst werden, wenn wir Nostr als Basis für die öffentliche Bildungsinfrastruktur einsetzen?
Material-Upload
- Es ist nicht einfach möglich OER bereitzustellen, sodass es auch auf verschiedenen Plattformen gefunden werden kann.
Mit Nostr als Basis-Infrastruktur würden die Metadaten und die Binärdaten nicht an den Service gekoppelt sein, von dem aus sie bereitgestellt wurden. Binärdaten können auf sogenannten Blossom-Servern gehostet werden. Metadaten, Kommentare und weitere textbasierte Daten werden über die Relay-Infrastruktur verteilt. Da Daten und Service entkoppelt sind, können die OER Materialien von verschiedenen Anwendungen aus konsumiert werden.
Kuration
- Es gibt keine interoperablen Sammlungen
- Metadaten-Annotation ist zentralisiert
- User können keine eigenen Metadaten hinzufügen
Sammlungen sind per se interoperabel. Auf Protokollebene ist definiert, wie Listen funktionieren. Die Annotation mit Metadaten ist an keiner Stelle zentralisiert. Das Versprechen der RDF-Community "Anyone can say anything about any topic" wird hier verwirklicht. Ich muss mir ja nicht alles anhören. Vielleicht konsumiere ich nur Metadaten-Events bestimmter Redaktionen oder User. Vielleicht nur diejenigen mit einer Nähe zu meinem sozialen Graphen. Jedenfalls gibt es die Möglichkeit für alle User entsprechende Metadaten bereit zu stellen.
Crawling, Indexierung und Suche * An vielen Stellen wird Content doppelt erschlossen, aber immer für die eigene Plattform * Es gibt keinen geteilten Datenraum, in den Akteure Content "pushen" können * Es gibt keine plattformübergreifenden Suchmöglichkeiten
Keine Doppelerschließungen mehr. Wenn ein User im Netzwerk ein Metadatenevent veröffentlicht hat, ist es für alle konsumierbar. Der Datenraum ist per se geteilt. Plattformübergreifende Suche wird durch die Kombination aus Relays und NIPs ermöglicht. In den NIPs können spezielle Query-Formate für die jeweiligen NIPs definiert werden. Relays können anzeigen, welche NIPs sie untersützten. Eine plattformübergreifende Suche ist im Nostr eine relay-übergreifende Suche.
Plattformübergreifende Kollaboration
- Obwohl nun #OEP in aller Munde sind, gibt es keine technischen Ansätze, wie (plattformübergreifende) Kollaboration technisch abgebildet werden kann
Nostr ist der technische Ansatz.
KI-Services
- KI-Services funktionieren oft nur auf der Plattform für die sie entwickelt werden
Es gibt im Nostr das Konzept der Data Vending Machines (s. auch data-vending-machines.org). Statt also einfach nur eine API zu bauen (was auch schon sehr schön ist, wenn sie offen zugänglich ist), könnten diese Services auch als Akteure im Nostr Netzwerk fungieren und Jobs annehmen und ausführen. Die Art der Jobs kann in einer Spezifikation beschrieben werden, sodass die Funktionsweise für alle interessierten Teilnehmer im Netzwerk einfach nachzuvollziehen ist.
Die Services könnten sogar monetarisiert werden, sodass sich hier auch Möglichkeiten böten, Geschäftsmodelle zu entwickeln.
Fazit
Die Open Education Community ist großartig. Es sind einzigartige und unglaublich engagierte Menschen, die sich dem hehren Ziel "Zugängliche Bildung für Alle" -> "Offene Bildung" verschrieben haben. Wir verwenden Creative Commons Lizenzen -> Commons -> Gemeingüter. Es ist okay, dass viele Projekte von Sponsoren und Förderungen abhängig sind. Was wir machen, ist im Sinne eines Gemeingutes: Öffentliche Bildung für alle. Also zahlen wir als Gemeinschaft alle dafür.
Was nicht okay ist: Dass das, wofür wir alle gezahlt haben, nach kurzer Zeit nicht mehr auffindbar ist. Dass es eingeschlossen wird. In öffentlich finanzierten Datensilos. Es muss für alle auch langfristig verfügbar sein. Sonst ist es nicht zugänglich, nicht offen. Dann ist das O in OER nur ein Label und Marketing, um für eine ABM-Maßnahme 3 Jahre Geld zu bekommen. Denn nichts anderes ist Content-Entwicklung, wenn der Content nach drei Jahren weggeschmissen wird.
Und dasselbe gilt für OEP. Offene Lernpraktiken, sind auch nur eine Phrase, wenn wir die passende technische Infrastruktur nicht mitdenken, die wirkliche Offenheit und Kollaboration und damit die Umsetzung offener Lernpraktiken ermöglicht.
Und wenn wir uns jetzt nicht Gedanken darüber machen, die Infrastruktur für offenes Lernen anzupassen, dann werden wir vermutlich in einigen Jahren sehen können, was bei politischen Umorientierungen noch davon übrig bleiben wird. Wenn die Fördertöpfe komplett gestrichen werden, was bleibt dann übrig von dem investierten Geld?
Wir brauchen Lösungen, die engagierte Communities weiter betreiben können und denen kein Kopf abgeschlagen werden kann, ohne dass wir zwei neue daneben setzen könnten.
Wir müssen uns jetzt Gedanken darüber machen.
Wie offen will öffentliche Bildungsinfrastruktur sein?
-
 @ d360efec:14907b5f
2025-05-31 00:36:48
@ d360efec:14907b5f
2025-05-31 00:36:48 -
 @ d360efec:14907b5f
2025-05-30 11:23:40
@ d360efec:14907b5f
2025-05-30 11:23:40 -
 @ 04c915da:3dfbecc9
2025-05-16 17:59:23
@ 04c915da:3dfbecc9
2025-05-16 17:59:23Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ 0b65f96a:7fda4c8f
2025-06-04 18:07:06
@ 0b65f96a:7fda4c8f
2025-06-04 18:07:06Es gibt Bibliotheken voll Literatur zur „Kunst“ der Kriegsführung. Dies hier ist ein Beitrag zu den Bibliotheken der Kunst Frieden zu führen. Denn Frieden ist nicht die Abwesenheit von Krieg. Sondern eine mindestens ebenso intensive Aktivität. Worin genau besteht sie aber? Ich glaube darin, weder nach der einen noch nach der anderen Seite vom Hochseil zu fallen. Denn vom Hochseil kann man immer nach zwei Seiten fallen. Das ist dann auch schon die Kernherausforderung: Gleichgewichthalten!
Es scheint zunächst ein ganz äußerlicher Auftrag. Es gibt immer und wird immer widerstreitende Interessen geben. Allerdings ist das nur die äußerste Zwiebelschale. Denn wenn wir die Sache etwas mit Abstand von uns selbst betrachten, werden wir in uns hinein verwiesen: Frieden kann nur von innen nach außen gestiftet werden. Wenn wir das Hochseil in uns suchen, was finden wir dann? – Zweifels ohne, wissen wir von uns, dass wir nicht jeden Tag unser bestes Selbst sind. Würde es sich nicht lohnen etwas genauer über die Möglichkeit nach zwei Seiten vom Hochseil zu fallen nachzudenken, zugunsten der eigenen Balancierfähigkeit?
Wir sind daran gewöhnt zu denken dem Guten steht das Böse gegenüber. Daraus ziehen ja alle Western und Martial Arts Streifen ihren Plot: Der Gute bringt den Bösen um die Ecke und damit hat wieder mal das Gute gesiegt. Wir bewerten das „um die Ecke bringen“ unterschiedlich, je nach dem, von wem es kommt.
Ich möchte einen neuen Gedanken vorschlagen über unser Inneres, über Gut und Böse nachzudenken. Denn, wie gesagt, vom Hochseil kann man nach zwei Seiten fallen. Und es hat immer drastische Wirkung. Wo kommen wir also hin, wenn wir sagen: Frieden ist immer ein Gleichgewichtszustand, ergo eine Zeit der Mitte?
Sagen wir Toleranz ist ein erstrebenswertes Ideal. Dann würden wir sicher sagen Engstirnigkeit ist das Gegenteil davon und alles andere als Wünschenswert. Ja, so ist es gewiss. Und es bleibt hinzuzufügen, auch Beliebigkeit ist das Gegenteil von Toleranz. Denn es gibt eine Grenze, wo Toleranz nicht mehr Toleranz ist, sondern Beliebigkeit, ein „alles ist möglich“. Ähnlich können wir es für Großzügigkeit denken: Großzügigkeit ist ein erstrebenswertes Ideal. Ihr Gegenteil ist Geiz. Ihr anderes Gegenteil die Verschwendung. Oder Mut. Mut ist ein erstrebenswertes Ideal. Feigheit sein Gegenteil. Sein anderes Gegenteil ist Leichtsinn. Mit andern Worten: Das Ideal wird immer zum Hochseil. Und wir können immer nach zwei Seiten von ihm fallen. Wenn wir diesem Gedanken folgen, kommen wir weg von der Gut-Böse-Dualität. Und stattdessen zur Frage nach dem Gleichgewicht. Zur Frage nach der Mittezeit.
Natürlich steht es uns frei all das zu denken. Oder auch nicht zu denken. Denn selbstverständlich ist es möglich es nicht zu denken und bei einer Dualitätsvorstellung festhängen zu bleiben. Es wird uns nur nicht helfen Frieden zu denken und in Frieden zu handeln. Wenn wir wollen können wir durch das Aufspannen einer Trinität einen neuen Raum eröffnen und betreten. In ihm wird Frieden aktiv führbar, denn er wird eine Gleichgewichtssituation in uns selbst! – Nicht eine, sich einander gegenüberstehender äußerer Mächte!
Gehen wir noch einen Schritt weiter in unserer Betrachtung, können wir feststellen, dass es durchaus einen Unterschied macht nach welcher Seite wir runter fallen. Denn auf der einen Seite ist es immer eine Verengung: Engstirnigkeit, Geiz, Feigheit in unseren Beispielen. Auf der anderen ist es immer eine Zersplitterung oder Versprühung. In unseren Beispielen Beliebigkeit, Verschwendung und Leichtsinn. Und das erstrebenswerte ist eben immer die Mitte, das von uns ständig aktualisierte Gleichgewicht.
Das interessante ist, wo diese Mitte liegt, lässt sich niemals statisch festlegen. Sie ist immer dynamisch. Denn sie kann zu unterschiedlichen Momenten an unterschiedlicher Stelle liegen. Es ist immer ein Ich, das sich in Geistesgegenwart neu ausbalanciert. Und darum ist Frieden so schwer. Wir werden ihn niemals „haben“, sondern ihm immer entgegen gehen.
Der Kriegsruf ist nichts anderes, als ein Versuch von denen, die vom Hochseil gefallen sind, uns auch herunter zu kicken.
Netter Versuch. Wird aber nichts!
In der Nussschale: Die Dualität auflösen in die Trinität der balancierenden Mitte zwischen der Geste der Versteinerung und der Geste des Zerstäubens oder Zersplitterns. Die dynamische Qualität der Mitte bemerken. Oder, tun wir es nicht, ist das gleich der erste Anstoß, der uns wieder zum Wackeln bringt. Und des Ich´s gewahr werden, das balanciert. Frieden führen ist eine Kunst.
Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
Patric I. Vogt, geb. 1968 in Mainz. Autor von „Zukunft beginnt im Kopf Ein Debattenbeitrag zur Kernsanierung von Rechtsstaat und Demokratie“. Lebt als freischaffender Künstler, Lehrer und Unternehmer. Über drei Jahrzehnte Beschäftigung mit dem Ideenfeld soziale #Dreigliederung und Anthroposophie. Moderation und Mediation von sozialen Prozessen und Organisationsentwicklung. Staatlich ungeprüft, abgesehen von den Fahrerlaubnissen zu Land und zu Wasser. Motto: Gedanken werden Worte, werden Taten! www.perspektivenwechsel.social
-
 @ a74cf7d3:37b9b82e
2025-06-05 17:03:04
@ a74cf7d3:37b9b82e
2025-06-05 17:03:04Lava is the most secure way to borrow against your bitcoin. Lava Loans allow you to borrow dollars using your bitcoin as collateral, all without giving up self-custody. No need to wait days, sign paperwork, bridge your bitcoin, or trust third-party custodians to take out a loan. All you have to do is set the terms of your loan within your Lava Vault, and you can get your loan capital within seconds.
Unlike other bitcoin-backed lending options, Lava is entirely self-custodial. You control your own keys and never have to transfer your bitcoin to a third party. Historically, most bitcoin-backed lending solutions required users to trust custodians with their bitcoin, exposing them to hacks, rehypothecation risk, insolvency, and seizures. This resulted in more than $24B in user funds lost in 2022 alone. Lending protocols on other chains like Ethereum or Solana require users to bridge their bitcoin, introducing additional custodial, bridge, smart contract, and platform risks. Both options are clunky, risky, and slow.
Lava Loans introduces a better model. We’ve built a borrowing protocol that works entirely on native bitcoin. Taking out a loan on Lava takes seconds, doesn't require paperwork, and allows you to maintain self-custody. Lava is the best option for simple, low-cost, and safe bitcoin-backed loans.
In this article we’ll dive into the key features of Lava Loans, how it is different from other borrowing options on the market, and explain how it works at a technical level.
Key Features of Lava
-
Instant loans: No paperwork. Just answer 2 questions and get your loan within seconds.
-
Low cost: We minimize costs by reducing loan risk, allowing us to offer the lowest rates on the market. All fees are made transparent at the start.
-
Flexible amounts: Borrow exactly what you need.
-
No Custodial Risk: Your BTC never leaves your control. There’s no risk of hacks, seizure, or rehypothecation. You can verify this yourself on-chain. Lava is the only loan product where you can independently verify—on-chain and in real time—that your bitcoin is not being rehypothecated.
-
No Loan Initiation Risk: Using atomic swaps, your collateral only moves if your loan capital is already secured.
-
No Repayment Risk: Repay your loan and your BTC is automatically returned, guaranteed by cryptography.
-
Reduced Liquidation Risk: You choose your own blinded, off-chain price source, minimizing the chance of unfair liquidation.
-
Bug-Minimized: Lava uses formally verified smart contracts on bitcoin (Discreet Log Contracts), meaning all contract outcomes are known and signed ahead of time. Execution is private and secure.
How It Works
The Lava Loans Protocol is built on top of bitcoin-native smart contracts, called Discreet Log Contracts (DLCs). DLCs enable conditional (oracle-based) contracts on bitcoin, meaning they can execute transactions based on pre-specified and approved conditions. Lava Loans are executed via custom DLCs that allow the borrower and lender to agree to the terms of a loan, enter into a contract based on those terms, and have the contract enforce the terms on-chain— all without requiring a third-party custodian.
DLCs allow for a trust-minimized borrowing experience, and they avoid many of the risks inherent with smart contracts on other platforms like Ethereum. DLCs operate on Bitcoin itself— you don’t need to move your coins to another chain or layer. They also mitigate bug risk because they are formally verified, meaning the output conditions of the contract are known from the beginning. This helps to avoid the exploits commonly seen in Ethereum. Because the contracts use off-chain oracles, they aren't susceptible to oracle manipulation by miners. Not only that, but these contracts are private, customizable (choose your own oracle), and scalable (minimal on-chain cost because execution happens off-chain).
Lava Loans are on-chain contracts between borrowers and lenders. The borrower and the lender agree on a loan amount (in USD), a collateral amount (in BTC), the loan duration, the interest rate, the loan-to-value (LTV) ratio at which liquidation happens, and a data feed (oracle) that will provide the Bitcoin price. When the contract is initialized, the collateral is locked and the loan capital is transferred to the borrower. The oracle feeds the price of Bitcoin into the contract on a continuous basis, and the contract executes according to its pre-defined parameters. As long as the borrower maintains a healthy LTV and repays their loan, their collateral is automatically returned to them upon completion.
Each Lava Loan goes through three phases:
Phase 1: Loan Initiation
- The loan is initialized via an atomic swap; the bitcoin collateral is locked in the smart contract and the loan capital is transferred from the lender to the borrower. Because this is done via an atomic swap, the borrower and lender do not have to trust one another or use an escrow. The collateral moves into the smart contract, and the loan capital is automatically sent to the borrower.
Phase 2: Active Loan
-
Once the atomic swap is complete, the loan is active. The bitcoin collateral remains locked in the smart contract, and the borrower has access to their loan capital.
-
While the loan is active, the oracle feeds the bitcoin price into the contract on an ongoing basis. This allows the contract to monitor the LTV.
Phase 3: Loan Termination
Once the loan is active, it can terminated in one of the following ways:
-
Repaid: If the borrower repays the loan, the collateral is released to the borrower atomically.
-
Liquidated: If the loan value reaches a pre-determined LTV or the borrower misses a payment, the collateral is immediately released to the lender for liquidation.
-
Expired: If the borrower does not repay the loan before the loan term ends, some of the collateral, equivalent to principal plus interest, is released to the lender, and the rest is sent to the borrower.
-
Fail-Safe: In rare scenarios where the loan process cannot be completed as expected due to unresponsive oracles, the protocol has built-in fail-safe mechanisms. These mechanisms ensure that the collateral is not lost.
As you can see, all of the loan terms and conditions are built into the smart contract. The borrower and lender agree on the terms, enter into the loan, and then the contract executes the pre-specified and approved transactions based on either the actions taken by the borrow/lender, or the price changes in BTC. As a user, you can verify at any point that your collateral sits on-chain, is locked in the contract, and isn’t being used or rehypothecated in any way.
Security
Lava Loans are designed to be the most secure option for Bitcoiners who want to borrow against their holdings. Lava’s approach is trust-minimized, bug-minimized, and verifiable for users.
Trust-Minimized
-
Traditional platforms expose you to bridge, custodian, or bank risk. Lava lets you borrow against native-BTC directly in your vault. This means there can’t be rehypothecation, funds lost in custodial hacks, or asset confiscation.
-
While other platforms require blind trust during loan initiation, Lava uses atomic swaps to ensure your BTC collateral only moves to the escrowed smart contract once the loan is in your hands.
-
The uncertainty of receiving collateral post-repayment is a concern with many platforms. Lava uses cryptographic guarantees to ensure that once you fulfill your repayment, your BTC is promptly returned.
-
You don’t have to trust a lender who can liquidate your BTC unjustly. With Lava, you choose your off-chain, blinded oracles per loan to provide price data, drastically reducing risks from malicious entities.
Bug-Minimized
-
Lava’s bitcoin smart contract is formally-verified, meaning the output conditions to the contract are known ahead of time, minimizing technical risk. DLCs, the underlying technology Lava uses, use pre-signed, encrypted transactions to specify the output conditions to a contract ahead of time. Since all the output conditions to the contract are specified ahead of time, and then encrypted using adaptor signatures, the output conditions are known (money can only move to borrower/lender).
-
Lava’s contracts have been audited by the best auditors in the industry, Antoine Riard from thelab31 and Conduition, as well as the core contributors to the cryptography behind DLCs.
Verifiable
-
Lava is the only loan product where you can independently verify—on-chain and in real time—that your bitcoin is not being rehypothecated. When you borrow using Lava, you have cryptographic proof, not just legal or reputational assurances, that your collateral is secure.
-
Lava’s oracle implementation is open-source.
-
Lava’s oracles make daily attestations and calculate a median price across various price feeds to avoid flash crash and unreliable margin call risk.
How Lava Compares

Loan Payments + Fees
Users who take out a Lava Loan pay a one-time origination fee (currently 2%) to open a loan, and each loan has a determined, fixed interest rate for the duration of the loan. Interest rates depend on the length of the loan, but they currently start at 5% annually. Users can also extend their loan by paying an extension fee (currently 2%) at the time that the loan is extended.
Loans that are longer than one month in duration require users to make monthly payments on their loans. Because the terms of Lava Loans are set programmatically in the smart contract, users must make their monthly payments on time in order to avoid being liquidated. You can make your monthly payments using digital dollars (either those held in your Lava Vault, or by depositing USDC into the vault) or via bank transfer. Bank transfers may take several days to clear, so it’s important to plan ahead in order to make the payments on time. Lava offers notifications in advance of payment deadlines in order to allow you sufficient time to plan and make payments.
FAQ
What are oracles?
Oracles are independent data feeds that attest to the price of Bitcoin and feed that price into the contract. At Lava, we’ve built Sibyls, an open-source oracle implementation for bitcoin. Users can choose their own oracles, and oracles have zero knowledge about the contracts they influence. In the case of the Lava Loans Protocol, oracles also make off-chain attestations, and in doing so, this helps us avoid the increased fees and miner manipulation that comes from on-chain oracles. You can learn more about our oracles here.
Why does Lava use digital dollars?
To ensure a fast, trust-minimized loan, Lava uses smart contracts that require HTLC compatibility. Fiat doesn’t support this, so we use digital dollars (like USDC on Solana) — which you can instantly withdraw to your bank account.
What are bitcoin smart contracts?
Bitcoin smart contracts (also known as discreet log contracts) enable conditional (oracle-based) contracts on bitcoin. The way it works is that each party to a contract creates and shares encrypted signatures for each output condition to the contract. Each counterparty has confidence they can decrypt the encrypted signatures and use them correctly at the right time because they can verify the encryption: verify when they can decrypt the signatures and that the signatures are valid.
Bitcoin smart contracts are a better way to do smart contracts because they are secure, private, customizable, and scalable. They mitigate bug risk because they are formally verified, meaning the output conditions of the contract are known from the beginning. This helps avoid exploits you constantly see in Ethereum. Since these contracts use off-chain oracles, they aren't susceptible to oracle manipulation by miners. Not only that, but these contracts are private, customizable (choose your own oracle), and scalable (minimal on-chain cost because execution happens off-chain).
These contracts are zero knowledge in that the blockchain has zero knowledge about the contract, the oracles have zero knowledge about the contract, and the counterparty can verify the encryption without needing the decrypted material.
Where can I learn more?
If you want to learn more about the Lava Loans Protocol, check out the loans paper here: https://github.com/lava-xyz/loans-paper/tree/main
Ready to borrow? Download the Lava Vault on iOS or Android and take out your first bitcoin-secured loan in seconds.
-
-
 @ 04c915da:3dfbecc9
2025-05-16 17:51:54
@ 04c915da:3dfbecc9
2025-05-16 17:51:54In much of the world, it is incredibly difficult to access U.S. dollars. Local currencies are often poorly managed and riddled with corruption. Billions of people demand a more reliable alternative. While the dollar has its own issues of corruption and mismanagement, it is widely regarded as superior to the fiat currencies it competes with globally. As a result, Tether has found massive success providing low cost, low friction access to dollars. Tether claims 400 million total users, is on track to add 200 million more this year, processes 8.1 million transactions daily, and facilitates $29 billion in daily transfers. Furthermore, their estimates suggest nearly 40% of users rely on it as a savings tool rather than just a transactional currency.
Tether’s rise has made the company a financial juggernaut. Last year alone, Tether raked in over $13 billion in profit, with a lean team of less than 100 employees. Their business model is elegantly simple: hold U.S. Treasuries and collect the interest. With over $113 billion in Treasuries, Tether has turned a straightforward concept into a profit machine.
Tether’s success has resulted in many competitors eager to claim a piece of the pie. This has triggered a massive venture capital grift cycle in USD tokens, with countless projects vying to dethrone Tether. Due to Tether’s entrenched network effect, these challengers face an uphill battle with little realistic chance of success. Most educated participants in the space likely recognize this reality but seem content to perpetuate the grift, hoping to cash out by dumping their equity positions on unsuspecting buyers before they realize the reality of the situation.
Historically, Tether’s greatest vulnerability has been U.S. government intervention. For over a decade, the company operated offshore with few allies in the U.S. establishment, making it a major target for regulatory action. That dynamic has shifted recently and Tether has seized the opportunity. By actively courting U.S. government support, Tether has fortified their position. This strategic move will likely cement their status as the dominant USD token for years to come.
While undeniably a great tool for the millions of users that rely on it, Tether is not without flaws. As a centralized, trusted third party, it holds the power to freeze or seize funds at its discretion. Corporate mismanagement or deliberate malpractice could also lead to massive losses at scale. In their goal of mitigating regulatory risk, Tether has deepened ties with law enforcement, mirroring some of the concerns of potential central bank digital currencies. In practice, Tether operates as a corporate CBDC alternative, collaborating with authorities to surveil and seize funds. The company proudly touts partnerships with leading surveillance firms and its own data reveals cooperation in over 1,000 law enforcement cases, with more than $2.5 billion in funds frozen.
The global demand for Tether is undeniable and the company’s profitability reflects its unrivaled success. Tether is owned and operated by bitcoiners and will likely continue to push forward strategic goals that help the movement as a whole. Recent efforts to mitigate the threat of U.S. government enforcement will likely solidify their network effect and stifle meaningful adoption of rival USD tokens or CBDCs. Yet, for all their achievements, Tether is simply a worse form of money than bitcoin. Tether requires trust in a centralized entity, while bitcoin can be saved or spent without permission. Furthermore, Tether is tied to the value of the US Dollar which is designed to lose purchasing power over time, while bitcoin, as a truly scarce asset, is designed to increase in purchasing power with adoption. As people awaken to the risks of Tether’s control, and the benefits bitcoin provides, bitcoin adoption will likely surpass it.
-
 @ d360efec:14907b5f
2025-05-27 15:46:26
@ d360efec:14907b5f
2025-05-27 15:46:26 -
 @ 2cde0e02:180a96b9
2025-06-05 15:13:03
@ 2cde0e02:180a96b9
2025-06-05 15:13:03pen & ink; monochromized
Magdalena Carmen Frida Kahlo y Calderón[a] (Spanish pronunciation: [ˈfɾiða ˈkalo]; 6 July 1907 – 13 July 1954[1]) was a Mexican painter known for her many portraits, self-portraits, and works inspired by the nature and artifacts of Mexico. Inspired by the country's popular culture, she employed a naïve folk art style to explore questions of identity, postcolonialism, gender, class, and race in Mexican society.[2] Her paintings often had strong autobiographical elements and mixed realism with fantasy. In addition to belonging to the post-revolutionary Mexicayotl movement, which sought to define a Mexican identity, Kahlo has been described as a surrealist or magical realist.[3] She is also known for painting about her experience of chronic pain.[4]
https://stacker.news/items/997980
-
 @ 20e7c953:3b8bcb21
2025-06-05 10:46:07
@ 20e7c953:3b8bcb21
2025-06-05 10:46:0721… That number means something. A reminder that limits create value - both in Bitcoin and in life.
Every June 21st, skaters around the world remind us that freedom is something you make yourself - one push at a time only constrained by your own limitations.
This year in Vientiane, we’re proud to support one of the few real skate spots in Laos. A place built and held together by skaters for skaters.
Expect around 50 locals - from young kids to older heads - showing up not just to skate, but to hold space for each other. No ego, no filters, just boards, fun and respect.
Bircoiners have lots to learn from these communities on this regard. Go skate and you'll find out.
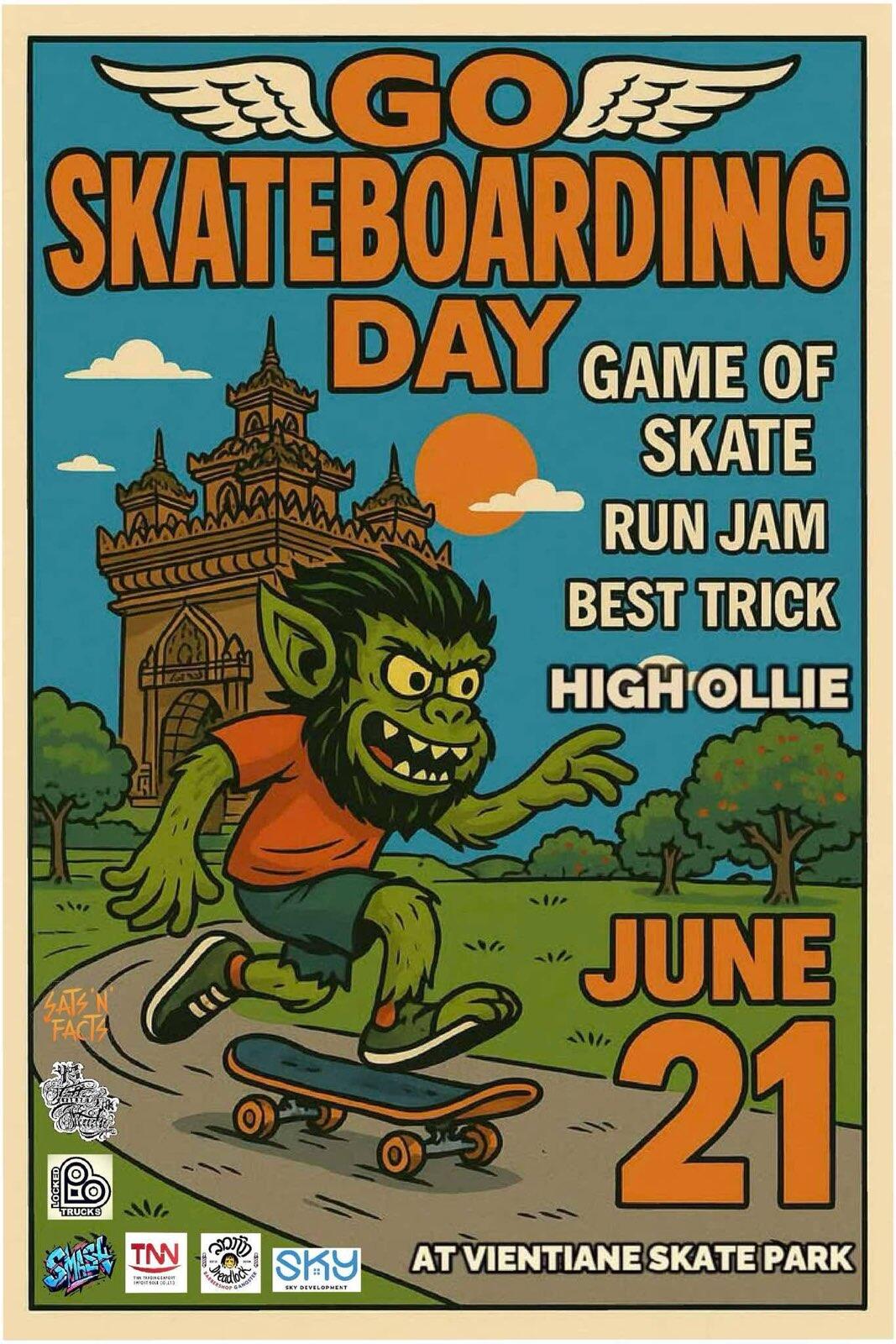
SnF
Laostr
Skateboardingisfun
Skate4Fun
Skatestr
-
 @ e2c72a5a:bfacb2ee
2025-06-05 16:54:43
@ e2c72a5a:bfacb2ee
2025-06-05 16:54:43Think your crypto is FDIC insured like your bank account? Big mistake. Crypto's wild west demands you be your own bank and security guard.
Crypto trading involves buying, selling, and exchanging digital currencies like Bitcoin or Ethereum, aiming to profit from price fluctuations. Security is paramount. Understand basic concepts like wallets (digital storage for your crypto), private keys (passwords to access your crypto), and blockchain (the technology that records all transactions).
Real world applications include using crypto for online purchases, international money transfers, and decentralized finance (DeFi) services like lending and borrowing. Current trends include the rise of DeFi, NFTs (non-fungible tokens), and increasing institutional investment.
Best practices? Use strong, unique passwords, enable two factor authentication (2FA) on all accounts, and store most of your crypto in cold wallets (offline storage) to protect against hacking. Be wary of phishing scams and fake websites. Never share your private keys or seed phrases.
Misconceptions? Crypto is not anonymous, transactions are not easily reversible, and past performance is not indicative of future results. Also, remember that regulations are evolving, so stay informed.
With crypto hacks on the rise, are you truly ready to secure your digital fortune, or are you leaving the door open for the next billion dollar heist?
-
 @ 04c915da:3dfbecc9
2025-05-16 17:12:05
@ 04c915da:3dfbecc9
2025-05-16 17:12:05One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 04c915da:3dfbecc9
2025-05-15 15:31:45
@ 04c915da:3dfbecc9
2025-05-15 15:31:45Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 975e4ad5:8d4847ce
2025-06-05 13:14:46
@ 975e4ad5:8d4847ce
2025-06-05 13:14:46What is the Fiat System and How Do Central Banks Set Interest Rates?
When central banks expand credit, they often increase the money supply by creating new money through mechanisms like quantitative easing (QE). For instance, a central bank may purchase government bonds, injecting money into the economy. This boosts liquidity but can lead to inflation when too much money chases limited goods and services.
Low interest rates make borrowing cheaper, encouraging spending and investment. However, this can overheat the economy, create speculative bubbles (e.g., in real estate), and drive inflation. Conversely, high interest rates restrict borrowing, slow the economy, and curb inflation but may trigger recessions.
How Would Interest Rates Work Under a Bitcoin Standard?
Under a Bitcoin standard, the money supply is fixed—only 21 million bitcoins will ever exist, with the last one mined around 2140. Unlike the fiat system, no central authority can manipulate the money supply or set interest rates. Instead, interest rates would be determined entirely by the market—by the supply and demand for capital.
If someone wants to borrow bitcoins, the interest rate would depend on negotiations between the lender and borrower. For example, if demand for loans is high and available bitcoins are scarce, interest rates would rise. Conversely, if there are ample bitcoin savings, rates might fall. This process would be fully decentralized and reflect real market conditions, not central bank decisions.
Since new bitcoins cannot be “printed,” there would be no inflation caused by an expanding money supply. Instead, bitcoin’s value would likely rise over time (deflation) as its fixed supply competes with growing demand. This could encourage saving over reckless spending, reshaping economic behavior.
Advantages of a Bitcoin Standard
-
Protection Against Inflation: Bitcoin’s fixed supply prevents currency devaluation, a common issue with fiat money. This safeguards savings and promotes long-term planning.
-
Decentralization: Without a central bank manipulating the market, economic decisions are made by individuals, not bureaucrats. This aligns with free-market principles where competition and innovation thrive.
-
Transparency and Security: The Bitcoin blockchain is public and immutable, ensuring transactions are transparent and secure from tampering.
-
Financial Freedom: Under a Bitcoin standard, individuals have full control over their money without government or bank interference, which is especially crucial in countries with unstable regimes or currencies.
-
Discipline in Lending: Without the ability to print money, lenders would be more cautious, reducing risky investments and speculative bubbles.
Potential Drawbacks and Why a Bitcoin Standard is Superior
One major argument against a Bitcoin standard is that it could slow economic growth. Low interest rates in the fiat system encourage borrowing and spending, driving economic activity. Under a Bitcoin standard, where interest rates are market-driven and likely higher, borrowing would be costlier, potentially limiting investments in new projects.
However, this critique misses a key point: economic growth fueled by artificially low interest rates and money printing is often unsustainable. It leads to debt crises, inflation, and bubbles that eventually burst, as seen in 2008. A Bitcoin standard promotes healthy economic discipline, where investments are based on real value, not artificial capital.
Moreover, bitcoin’s deflationary nature could shift how people view money. Instead of chasing endless growth, societies might prioritize sustainability, innovation, and efficiency. This could lead to a more stable and equitable economy in the long run.
Additional Considerations
A Bitcoin standard could transform global trade. Today, countries with fiat currencies often manipulate exchange rates to gain trade advantages. With bitcoin as a universal currency, such manipulations would vanish, fostering fairer competition.
Another aspect is energy efficiency. While bitcoin mining consumes energy, it incentivizes the development of renewable sources as miners seek cheap, sustainable energy. This could accelerate the transition to a green economy.
Conclusion
The Bitcoin standard offers a vision of an economy rooted in sound money, free markets, and financial freedom. While it may slow certain aspects of economic growth, it creates a more stable and sustainable system that protects individuals from inflation and centralized control. In a world where trust in institutions is waning, the Bitcoin standard is a step toward a fairer and more transparent future.
-
-
 @ 8d34bd24:414be32b
2025-06-04 13:21:20
@ 8d34bd24:414be32b
2025-06-04 13:21:20It is hard going through difficult situations. Health problems, family problems, financial problems, feeling alone, feeling stuck in the wrong place, and persecution are all situations that Christians regularly find themselves. The question is “How will we respond to pain?”
Advice for the Suffering
Some Christians pull away from God when it feels like everything is going wrong. They think God doesn’t care or can’t fix things. They resent every minute of pain and accuse God of wrongdoing. Even Job, who fell on his face in worship after losing everything had a moment of weakness.
“Oh that my grief were actually weighed\ And laid in the balances together with my calamity!\ For then it would be heavier than the sand of the seas;\ Therefore my words have been rash.” (Job 6:2-3) {emphasis mine}
After a moment of doubt, he did, however, repent of his rash words, as should we all.
Job should be an example to us all in dealing with pain and difficult situations. This is the verse that inspired this post.
But it is still my consolation,\ And I rejoice in unsparing pain,\ That I have not denied the words of the Holy One. \ (Job 6:10) {emphasis mine}
What an example! “I rejoice in unsparing pain.” When we trust God so much that we can rejoice in unsparing pain, we are trusting God as we should. We are accepting that God is working good in our life and we can trust Him even when nothing makes sense to us.
I also love how he says that his consolation is that “I have not denied the words of the Holy One.” Job is hurting terribly. His heart is broken. He is destitute. He lost 8 children in one day. His friends, that came to console him, have instead accused him of wrongdoing. He doesn’t understand what God is doing and why, but he has “NOT denied the words of the Holy One.” He is still putting his faith in God and his word. He is still submitting to God when he feels mistreated. He is still trusting \ God, even when he doesn’t understand what God is doing and why so many bad things are raining down on him in a torrent. Despite it all, he refuses to deny God. I hope if I am ever put through similar situations, that I can trust God and not deny His goodness.
Advice for friends
The book of Job, in addition to advice to those who are suffering, also gives advice to friends of those who are suffering. (or maybe more accurately, what not to do)
Job’s friends came with the intention to encourage and console Job. Every time Job would confess his thoughts, concerns, and questions, the response by his friends would get harsher and harsher. In the beginning they were gentle corrections, but they quickly escalated to accusing Job of great sins, that they had to know were not true, and blaming Job for every hard thing that had happened to him.
I’ve talked to other Christians who have confessed to being dragged down by other Christians who would tell them that every difficult thing that happened to them was due to their sin or lack of faith. In the case of Job, his difficulties were due to his faithfulness, in order to prove to Satan and all of history that a faithful man would stay faithful to God in good times and in bad.
Can Christians suffer as a consequence of sins and poor decisions? Of course, but there are many times that the faithful suffer. In Scripture, the people who suffered most were frequently the most faithful.
Job’s correction of his friends was accurate.
“For the despairing man there should be kindness from his friend;\ So that he does not forsake the fear of the Almighty.\ My brothers have acted deceitfully like a wadi,\ Like the torrents of wadis which vanish, (Job 6:14-15)
For those who don’t know, a wadi is a streambed that has water running in the wet season, but is bone dry during the dry season. Job accused his friends of being encouraging and helpful when he was prospering, then showing up and providing no encouragement or help when he needed it most. He thought refreshment was coming to visit, and instead what hope he had left was drained from him by his “friends.”
We need to make sure we aren’t one of those who decreases hope and decreases faith in one who is hurting. We need to have mercy when a hurting person works through their confusion and doubts and help lead them back to God instead of driving a wedge between them and God.
May the God of heaven protect us and lead us through the trials of life and may our trials lead us into the arms of our Savior. May God help us to merciful and to help guide the hurting into the Savior’s care.
Trust Jesus
-
 @ e2c72a5a:bfacb2ee
2025-06-05 16:50:08
@ e2c72a5a:bfacb2ee
2025-06-05 16:50:08Think crypto is just magic internet money? Think again.
Tokenomics is the secret sauce that makes or breaks a crypto project. It is the study of how tokens are created, distributed, and used within a blockchain ecosystem. Imagine it as the economic policy of a digital nation, dictating everything from supply and demand to user incentives.
Key features include supply caps, distribution models, utility, and burn mechanisms. A well designed token economy incentivizes user behavior, secures the network, and fosters long term growth. Poor tokenomics? It can lead to manipulation and project failure.
Zero Knowledge Proofs are like showing you know a password without revealing the password itself. This tech allows for private and secure transactions, verifying data without exposing the data itself. Think of voting systems where your vote stays secret, or supply chains where product details are confirmed without revealing the supplier.
Want to dive deeper into the economics of crypto? What project has the most interesting tokenomics you have seen?
-
 @ a5142938:0ef19da3
2025-06-05 10:24:37
@ a5142938:0ef19da3
2025-06-05 10:24:37Brands
Nordkidz is a German brand that creates made-to-order clothing and linens for babies, children, and a little bit for their parents.
Natural materials used in products
⚠️ Warning: some products from this brand contain non-natural materials, including:
Categories of products offered
This brand offers products made entirely from natural materials in the following categories:
Clothing
- Clothing fits : babies, children, unisex
- Tops : sweaters, t-shirts
- Bottoms : pants-trousers, shorts, sweatpants
- Head & handwear : hats, scarves
Home
- Linen : bath ponchos, bean bag covers, muslin squares
Other information
👉 Learn more on the brand website
Where to find their products?
- Nordkidz (in German, delivery area: Germany and the European Union) 💚 Via this link, you directly support the brand.
📝 You can contribute to this entry by suggesting edits in comments.
🗣️ Do you use this brand's products? Share your opinion in the comments.
⚡ Happy to have found this information? Support the project by making a donation to thank the contributors.
-
 @ 21335073:a244b1ad
2025-05-09 13:56:57
@ 21335073:a244b1ad
2025-05-09 13:56:57Someone asked for my thoughts, so I’ll share them thoughtfully. I’m not here to dictate how to promote Nostr—I’m still learning about it myself. While I’m not new to Nostr, freedom tech is a newer space for me. I’m skilled at advocating for topics I deeply understand, but freedom tech isn’t my expertise, so take my words with a grain of salt. Nothing I say is set in stone.
Those who need Nostr the most are the ones most vulnerable to censorship on other platforms right now. Reaching them requires real-time awareness of global issues and the dynamic relationships between governments and tech providers, which can shift suddenly. Effective Nostr promoters must grasp this and adapt quickly.
The best messengers are people from or closely tied to these at-risk regions—those who truly understand the local political and cultural dynamics. They can connect with those in need when tensions rise. Ideal promoters are rational, trustworthy, passionate about Nostr, but above all, dedicated to amplifying people’s voices when it matters most.
Forget influencers, corporate-backed figures, or traditional online PR—it comes off as inauthentic, corny, desperate and forced. Nostr’s promotion should be grassroots and organic, driven by a few passionate individuals who believe in Nostr and the communities they serve.
The idea that “people won’t join Nostr due to lack of reach” is nonsense. Everyone knows X’s “reach” is mostly with bots. If humans want real conversations, Nostr is the place. X is great for propaganda, but Nostr is for the authentic voices of the people.
Those spreading Nostr must be so passionate they’re willing to onboard others, which is time-consuming but rewarding for the right person. They’ll need to make Nostr and onboarding a core part of who they are. I see no issue with that level of dedication. I’ve been known to get that way myself at times. It’s fun for some folks.
With love, I suggest not adding Bitcoin promotion with Nostr outreach. Zaps already integrate that element naturally. (Still promote within the Bitcoin ecosystem, but this is about reaching vulnerable voices who needed Nostr yesterday.)
To promote Nostr, forget conventional strategies. “Influencers” aren’t the answer. “Influencers” are not the future. A trusted local community member has real influence—reach them. Connect with people seeking Nostr’s benefits but lacking the technical language to express it. This means some in the Nostr community might need to step outside of the Bitcoin bubble, which is uncomfortable but necessary. Thank you in advance to those who are willing to do that.
I don’t know who is paid to promote Nostr, if anyone. This piece isn’t shade. But it’s exhausting to see innocent voices globally silenced on corporate platforms like X while Nostr exists. Last night, I wondered: how many more voices must be censored before the Nostr community gets uncomfortable and thinks creatively to reach the vulnerable?
A warning: the global need for censorship-resistant social media is undeniable. If Nostr doesn’t make itself known, something else will fill that void. Let’s start this conversation.
-
 @ e2c72a5a:bfacb2ee
2025-06-05 16:46:19
@ e2c72a5a:bfacb2ee
2025-06-05 16:46:19Think proving you're over 21 without showing your ID is impossible? Zero Knowledge Proofs make it real.
Zero Knowledge Proofs let you prove something is true without revealing the information itself. Imagine proving you know a password without saying it. It's like magic, but it's math.
They're used in crypto for private transactions, secure voting, and faster blockchains. Zcash and Aztec use them to hide transaction details. StarkWare uses them to make Ethereum faster.
But here's the twist: zk STARKs don't need a trusted setup, unlike zk SNARKs. This makes them more secure and decentralized.
Misconception alert: ZKPs aren't just for privacy. They also boost scalability and interoperability.
Want to dive deeper into this mind bending tech? What other secrets can ZKPs unlock?
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ cae03c48:2a7d6671
2025-06-05 16:01:20
@ cae03c48:2a7d6671
2025-06-05 16:01:20Bitcoin Magazine
Adam Back Invests SEK 21 Million to H100 Group Bitcoin Treasury StrategyToday, H100 Group AB announced it has entered a SEK 21 million convertible loan from an investment agreement with Adam Back, with the option to expand his investment to SEK 277 million through a five-tranche convertible loan deal. The proceeds will be used to buy Bitcoin in alignment with H100 Group’s long-term Bitcoin treasury strategy.
H100 Group AB (Ticker: H100) secures a SEK 21M ($2.1M) commitment from @adam3us , with rights to invest an additional SEK 128M ($12.8M) in tranches—bringing the total contemplated raise to SEK 277M (~$27.7M). pic.twitter.com/c0HgMSRxut
— H100 (@H100Group) June 3, 2025
Under the agreement, Back may invest up to SEK 128 million across four additional tranches, with guaranteed participation of at least 50%. Each tranche is twice his committed amount, demonstrating his support for H100’s long-term growth.
The press release said, “Adam Back may request the Second Tranche within 90 days from signing of the Initial Tranche, the Third Tranche within 90 days from signing of the Second Tranche, the Fourth Tranche within 90 days from signing of the Third Tranche and the Fifth Tranche within ninety 90 days from signing of the Fourth Tranche. In the event Adam Back does not request a Future Tranche within the deadline, the right to request subsequent Future Tranches lapses.”
The convertible loans have no interest and have a five year maturity. At any time, Back may convert the loans into shares of the Company. Conversion prices are fixed per tranche: SEK 1.75 per share for the initial tranche, rising to SEK 5.00 by the fifth tranche. H100 retains the right to force conversion if the stock price exceeds the conversion rate by 33% over a 20 day period. Full conversion of the initial tranche would result in 12 million new shares and a 9.3% dilution.
“Upon request of a tranche Adam Back is obliged to invest in the relevant Tranche with SEK 15,750,000 in the second tranche, SEK 23,625,000 in the third tranche, SEK 35,437,500 in the fourth tranche, and SEK 53,156,250 in the fifth tranche,” stated the press release. “The contemplated size for each tranche is twice the entitled amount of Adam Back.”
Blockstream has “been around since 2014 and we work with our investors to put Bitcoin in a balance sheet back then and since then,” said Adam Back at the 2025 Bitcoin Conference. “I think the way to look at the treasury companies is that Bitcoin is effectively the hurdle rate; it’s very hard to outperform bitcoin. Most people that have invested in things since bitcoin has been around have thought, ‘oh, I should have put that in bitcoin and not in the other thing.”
This post Adam Back Invests SEK 21 Million to H100 Group Bitcoin Treasury Strategy first appeared on Bitcoin Magazine and is written by Oscar Zarraga Perez.
-
 @ b1ddb4d7:471244e7
2025-06-04 11:01:29
@ b1ddb4d7:471244e7
2025-06-04 11:01:29Bitcoin FilmFest (BFF25) returns to Warsaw for its third edition, blending independent cinema—from feature films and commercials to AI-driven experimental visuals—with education and entertainment.
Hundreds of attendees from around the world will gather for three days of screenings, discussions, workshops, and networking at the iconic Kinoteka Cinema (PKiN), the same venue that hosted the festival’s first two editions in March 2023 and April 2024.
This year’s festival, themed “Beyond the Frame,” introduces new dimensions to its program, including an extra day on May 22 to celebrate Bitcoin Pizza Day, the first real-world bitcoin transaction, with what promises to be one of Europe’s largest commemorations of this milestone.
BFF25 bridges independent film, culture, and technology, with a bold focus on decentralized storytelling and creative expression. As a community-driven cultural experience with a slightly rebellious spirit, Bitcoin FilmFest goes beyond movies, yet cinema remains at its heart.
Here’s a sneak peek at the lineup, specially curated for movie buffs:
 Generative Cinema – A special slot with exclusive shorts and a thematic debate on the intersection of AI and filmmaking. Featured titles include, for example: BREAK FREE, SATOSHI: THE CREATION OF BITCOIN, STRANGE CURRENCIES, and BITCOIN IS THE MYCELIUM OF MONEY, exploring financial independence, traps of the fiat system, and a better future built on sound money.
Generative Cinema – A special slot with exclusive shorts and a thematic debate on the intersection of AI and filmmaking. Featured titles include, for example: BREAK FREE, SATOSHI: THE CREATION OF BITCOIN, STRANGE CURRENCIES, and BITCOIN IS THE MYCELIUM OF MONEY, exploring financial independence, traps of the fiat system, and a better future built on sound money. Upcoming Productions Preview – A bit over an hour-long block of unreleased pilots and works-in-progress. Attendees will get exclusive first looks at projects like FINDING HOME (a travel-meets-personal-journey series), PARALLEL SPACES (a story about alternative communities), and THE LEGEND OF LANDI (a mysterious narrative).
Upcoming Productions Preview – A bit over an hour-long block of unreleased pilots and works-in-progress. Attendees will get exclusive first looks at projects like FINDING HOME (a travel-meets-personal-journey series), PARALLEL SPACES (a story about alternative communities), and THE LEGEND OF LANDI (a mysterious narrative). Freedom-Focused Ads & Campaigns – Unique screenings of video commercials, animations, and visual projects, culminating in “The PoWies” (Proof of Work-ies)—the first ever awards show honoring the best Bitcoin-only awareness campaigns.
Freedom-Focused Ads & Campaigns – Unique screenings of video commercials, animations, and visual projects, culminating in “The PoWies” (Proof of Work-ies)—the first ever awards show honoring the best Bitcoin-only awareness campaigns.To get an idea of what might come up at the event, here, you can preview 6 selected ads combined into two 2 videos:
 Open Pitch Competition – A chance for filmmakers to present fresh ideas and unfinished projects to an audience of a dedicated jury, movie fans and potential collaborators. This competitive block isn’t just entertaining—it’s a real opportunity for creators to secure funding and partnerships.
Open Pitch Competition – A chance for filmmakers to present fresh ideas and unfinished projects to an audience of a dedicated jury, movie fans and potential collaborators. This competitive block isn’t just entertaining—it’s a real opportunity for creators to secure funding and partnerships. Golden Rabbit Awards: A lively gala honoring films from the festival’s Official Selection, with awards in categories like Best Feature, Best Story, Best Short, and Audience Choice.
Golden Rabbit Awards: A lively gala honoring films from the festival’s Official Selection, with awards in categories like Best Feature, Best Story, Best Short, and Audience Choice.BFF25 Main Screenings
Sample titles from BFF25’s Official Selection:
 REVOLUCIÓN BITCOIN – A documentary by Juan Pablo, making its first screening outside the Spanish-speaking world in Warsaw this May. Three years of important work, 80 powerful minutes to experience. The film explores Bitcoin’s impact across Argentina, Colombia, Mexico, El Salvador, and Spain through around 40 diverse perspectives. Screening in Spanish with English subtitles, followed by a Q&A with the director.
REVOLUCIÓN BITCOIN – A documentary by Juan Pablo, making its first screening outside the Spanish-speaking world in Warsaw this May. Three years of important work, 80 powerful minutes to experience. The film explores Bitcoin’s impact across Argentina, Colombia, Mexico, El Salvador, and Spain through around 40 diverse perspectives. Screening in Spanish with English subtitles, followed by a Q&A with the director. UNBANKABLE – Luke Willms’ directorial debut, drawing from his multicultural roots and his father’s pioneering HIV/AIDS research. An investigative documentary based on Luke’s journeys through seven African countries, diving into financial experiments and innovations—from mobile money and digital lending to Bitcoin—raising smart questions and offering potential lessons for the West. Its May appearance at BFF25 marks its largest European event to date, following festival screenings and nominations across multiple continents over the past year.
UNBANKABLE – Luke Willms’ directorial debut, drawing from his multicultural roots and his father’s pioneering HIV/AIDS research. An investigative documentary based on Luke’s journeys through seven African countries, diving into financial experiments and innovations—from mobile money and digital lending to Bitcoin—raising smart questions and offering potential lessons for the West. Its May appearance at BFF25 marks its largest European event to date, following festival screenings and nominations across multiple continents over the past year. HOTEL BITCOIN – A Spanish comedy directed by Manuel Sanabria and Carlos “Pocho” Villaverde. Four friends, 4,000 bitcoins , and one laptop spark a chaotic adventure of parties, love, crime, and a dash of madness. Exploring sound money, value, and relationships through a twisting plot. The film premiered at the Tarazona and Moncayo Comedy Film Festival in August 2024. Its Warsaw screening at BFF25 (in Spanish with English subtitles) marks its first public showing outside the Spanish-speaking world.
HOTEL BITCOIN – A Spanish comedy directed by Manuel Sanabria and Carlos “Pocho” Villaverde. Four friends, 4,000 bitcoins , and one laptop spark a chaotic adventure of parties, love, crime, and a dash of madness. Exploring sound money, value, and relationships through a twisting plot. The film premiered at the Tarazona and Moncayo Comedy Film Festival in August 2024. Its Warsaw screening at BFF25 (in Spanish with English subtitles) marks its first public showing outside the Spanish-speaking world.Check out trailers for this year’s BFF25 and past editions on YouTube.
Tickets & Info:
- Detailed program and tickets are available at bitcoinfilmfest.com/bff25.
- Stay updated via the festival’s official channels (links provided on the website).
- Use ‘LN-NEWS’ to get 10% of tickets
-
 @ 4fa5d1c4:fd6c6e41
2025-06-04 17:45:05
@ 4fa5d1c4:fd6c6e41
2025-06-04 17:45:051. Einleitung
Dieser Beitrag bietet eine detaillierte Einführung in Nostr - ein dezentrales Protokoll für soziale Medien, das sich grundlegend von traditionellen und föderierten Plattformen unterscheidet - und erweitert seine Diskussion, um das Potenzial für die Integration von Nostr in die Entwicklung von Bildungsplattformen im Sinne von Open Educational Practices (OEP) zu untersuchen. Nostr ist als leichtgewichtiger, zensurresistenter Mechanismus konzipiert, der in erster Linie auf einer kryptografischen Schlüsselverwaltung und einer Client-zentrierten Architektur basiert, die zusammen eine dezentrale Identitätskontrolle und Autonomie über digitale Inhalte ermöglichen. Im Gegensatz zu konventionellen zentralisierten Modellen, die sich auf servergestützte Kontrolle oder föderierte Systeme wie Mastodon, die Moderation und Identitätsspeicherung zusammenfassen, stützt sich Nostr auf ein Netzwerk von "Relais", die ohne direkte Interkommunikation arbeiten, wobei alle Funktionen der Datenaggregation, des Austauschs von Inhalten zwischen den Räumen und der Benutzerinteraktion an die Client-Anwendungen delegiert werden. Ziel dieses Beitrags ist es daher, einen umfassenden technischen und konzeptionellen Überblick über die Architektur des Protokolls und eine kritische Diskussion seiner Anwendbarkeit im Kontext dezentraler Bildungsplattformen zu geben, die eine offene, nutzergesteuerte Erstellung, Verwaltung und Verteilung von Inhalten fördern und damit den Prinzipien des OEP entsprechen.
2. Hintergrund und Motivation
Die Entwicklung der sozialen Medien in den letzten zwei Jahrzehnten war geprägt von zunehmend zentralisierten Plattformen, die sowohl die digitale Identität der Nutzer als auch die von ihnen erstellten Inhalte kontrollieren, was oft zu Zensur, algorithmischer Manipulation und Einzelausfällen führt. Im Gegensatz dazu haben sich dezentralisierte Social-Media-Protokolle wie Nostr als innovative Antwort auf diese Zentralisierungsfallen entwickelt, die offene, kryptografisch sichere und verteilte Architekturen verwenden. Nostr wurde mit dem ausdrücklichen Schwerpunkt konzipiert, den Nutzern die volle Kontrolle über ihre Kontoauthentifizierung und digitale Identität zu geben, was durch die Verwaltung von kryptografischen Schlüsselpaaren analog zu denen in Bitcoin-Wallets erreicht wird. Dieses Modell verbessert nicht nur die zensurresistenten Eigenschaften der Plattform, sondern verändert auch grundlegend die Machtdynamik in traditionellen sozialen Netzwerken, da es die Abhängigkeit von zentralen Behörden minimiert und die Möglichkeiten der Ausbeutung und Überwachung verringert. Im Kontext von Bildungsökosystemen bieten diese Merkmale eine solide Grundlage für die Entwicklung von Plattformen, die transparent, partizipatorisch und widerstandsfähig sind, da sie die gemeinsame Nutzung und kontinuierliche Weiterentwicklung von Bildungsressourcen ohne zentralisierte Kontrolle oder Unternehmenssteuerung unterstützen.
3. Technische Architektur von Nostr
Die Architektur von Nostr basiert in erster Linie auf zwei integralen Komponenten: Clients und Relays. Clients sind die benutzerseitigen Anwendungen, die die Erstellung, Veröffentlichung und Aggregation von Inhalten ermöglichen, während Relays Server sind, die von den Benutzern generierte Nachrichten, so genannte "Events", empfangen, speichern und weiterleiten. Eine der wichtigsten Neuerungen des Nostr-Protokolls ist die radikale Entkopplung der traditionellen Client-Server-Beziehung: Die Relais müssen sich nicht synchronisieren oder miteinander kommunizieren, was bedeutet, dass die Replikation von Inhalten und die Aggregation von Daten zwischen den Räumen vollständig auf der Client-Seite stattfindet. Dies minimiert die zentrale Kontrolle und schafft ein verteiltes, relaisbasiertes System, das von Natur aus resistent gegen Zensur ist, da die Dichte der verfügbaren Relays und die Möglichkeit der Nutzer, sich mit mehreren Relays zu verbinden, sicherstellen, dass die Inhalte auch dann zugänglich bleiben, wenn bestimmte Relays ausfallen oder kompromittiert sind.
In Nostr sind Ereignisse als JSON-Objekte strukturiert, die einem definierten Schema mit verschiedenen "Arten" (NIPs) entsprechen, um spezifische Funktionalitäten und andere zukünftige Erweiterungen zu unterstützen. Jedes Ereignis wird mit dem privaten kryptografischen Schlüssel des Nutzers digital signiert, was die Authentizität und Integrität der Daten garantiert und gleichzeitig eine sichere, pseudonyme Interaktion ermöglicht. Da innerhalb des Protokolls keine zentrale Behörde oder ein einziger Identitätsspeicher existiert, behalten die Nutzer die vollständige Kontrolle über ihre digitalen Identitäten, und wenn der private Schlüssel verloren geht, ist das entsprechende Konto unwiederbringlich. Dieser Ansatz verankert den Grundsatz, dass Identität sowohl dezentralisiert als auch unveränderlich ist, und stärkt die individuelle Kontrolle über persönliche Daten und Inhalte.
Da die Relays unabhängig voneinander von verschiedenen Betreibern verwaltet und nicht von zentralen Diensten koordiniert werden, können die Benutzer mehrere Relays auswählen, um die Bereitstellung und Replikation von Inhalten zu optimieren. Diese architektonische Entscheidung verbessert die Redundanz und Ausfallsicherheit erheblich, bringt aber gleichzeitig technische Herausforderungen in Bezug auf Standardisierung, Moderation und effiziente Kommunikation zwischen den Clients mit sich. Nostr integriert auch Bitcoin-basierte Mikrozahlungen (bekannt als "Zaps"), um finanzielle Anreize für den Betrieb von Relay-Servern zu schaffen und so die Herausforderungen der wirtschaftlichen Nachhaltigkeit in einer dezentralen Infrastruktur zu bewältigen. Die Design-Entscheidungen in Nostr fördern Offenheit und Innovation, indem sie es jeder Person oder Organisation mit ausreichenden technischen Fähigkeiten erlauben, ein Relay zu hosten oder einen Client zu entwickeln, was zu einem lebendigen Ökosystem von verschiedenen Anwendungen und Diensten führt.
4. Identitätsmanagement und Moderation
Im Mittelpunkt des dezentralen Paradigmas von Nostr steht der Ansatz der Identitätsverwaltung, der sich von traditionellen Systemen unterscheidet, bei denen Identitäten als Kontodaten von zentralen Servern verwaltet werden. Bei Nostr verfügt jeder Benutzer über ein einzigartiges kryptografisches Schlüsselpaar, wobei der öffentliche Schlüssel als dauerhafte digitale Kennung und der private Schlüssel als Mittel zum Signieren aller Aktionen und Ereignisse dient. Dieses kryptonative Modell gewährleistet nicht nur robuste Sicherheit und Authentizität, sondern überlässt den Nutzern auch die alleinige Verantwortung für die Verwaltung ihrer Schlüssel - was sowohl die Freiheit als auch das Risiko eines vollständig dezentralen Identitätssystems unterstreicht.Dieses empfindliche Gleichgewicht unterstreicht die Autonomie der Nutzer und steht im Einklang mit dem breiteren Ethos dezentraler sozialer Medien, in denen keine einzelne Instanz die Identität einer Person ohne Zugang zu ihrem privaten Schlüssel außer Kraft setzen oder manipulieren kann.
Die Moderation in Nostr ist aufgrund des dezentralen Kuratierungsmodells noch komplexer. Die Inhalte werden nicht von einer zentralen Behörde moderiert, sondern durch eine Kombination aus relaisspezifischen Richtlinien und clientseitigen Kontrollen, wie z. B. benutzerdefinierte Listen für persönliche Kuratoren oder Sperr-/Stummschaltungsfunktionen. Dieser Ansatz fördert zwar die freie Meinungsäußerung und unterstützt eine Vielzahl von Standpunkten, kann aber auch zu uneinheitlichen Moderationsrichtlinien und fragmentierten Nutzererfahrungen auf verschiedenen Relays und Clients führen, was für die Nutzer eine erhebliche technische und verhaltensbezogene Belastung darstellt, wenn sie ihre digitalen Umgebungen kuratieren wollen.
5. Skalierbarkeit und Widerstandsfähigkeit gegen Zensur
Ein entscheidendes Merkmal des Nostr-Protokolls ist sein hohes Maß an Skalierbarkeit und Zensurresistenz, das durch seine verteilte, relaisbasierte Architektur erreicht wird. Durch die Dezentralisierung der Speicherung und Verbreitung von Inhalten auf zahlreiche unabhängige Relays entschärft Nostr die üblichen Schwachstellen zentralisierter sozialer Plattformen, wie z. B. Single Points of Failure oder das Potenzial für staatliche oder unternehmensgesteuerte Zensur. Mehrere Relays können gleichzeitig arbeiten, wodurch sichergestellt wird, dass die Stabilität des Netzwerks auch dann erhalten bleibt, wenn einige von ihnen vom Netz genommen werden oder behördlichem Druck ausgesetzt sind, und dass Inhalte für Kunden, die mit alternativen Relays verbunden sind, zugänglich bleiben.
Die Skalierbarkeit von Nostr wird dadurch verbessert, dass sich die Nutzenden gleichzeitig mit mehreren Relays verbinden können, was die Replikation von Inhalten über ein globales Netz von Servern ermöglicht, das sich über zahlreiche geografische Regionen und autonome Systeme erstreckt. Dieser Replikationsmechanismus bringt jedoch Herausforderungen mit sich, wie z. B. eine erhöhte Redundanz bei der Speicher- und Bandbreitennutzung, die eine sorgfältige Optimierung und die Entwicklung innovativer clientseitiger Strategien erfordern, um den Datenabruf zu verwalten und den Overhead zu reduzieren, ohne die Verfügbarkeit zu beeinträchtigen. Darüber hinaus trägt die Dezentralisierung der Zuständigkeiten für Kuratierung und Moderation zu einer dynamischen Umgebung bei, in der Inhalte sowohl gegen erzwungene Löschungen resistent als auch an die Bedürfnisse der Nutzer anpassbar sind, wenn auch auf Kosten von Einheitlichkeit und vorhersehbarer Nutzererfahrung.
6. Vergleich mit föderierten und zentralisierten Modellen
Das Aufkommen dezentraler Protokolle wie Nostr steht in scharfem Kontrast zu föderierten Netzwerken wie Mastodon, die das ActivityPub-Protokoll verwenden. Während föderierte Systeme die Kontrolle über unabhängige Instanzen verteilen, verlassen sie sich immer noch auf ein gewisses Maß an Zentralisierung auf der Ebene jeder einzelnen Instanz, von denen jede ihre eigenen Richtlinien bezüglich Moderation, Identitätsüberprüfung und Inhaltszensur durchsetzt. In diesen Systemen ist die Verwaltung zwar auf mehrere Knotenpunkte verteilt, aber es besteht eine Abhängigkeit von Serveradministratoren, die erhebliche Macht über den Inhalt und die Identität der Benutzer haben; dies steht im Gegensatz zu Nostrs vollständig kundenorientiertem Kurations- und Identitätsverwaltungsmodell, das darauf abzielt, jeden einzelnen Kontrollpunkt zu eliminieren.
In zentralisierten Architekturen werden Benutzerdaten und -identitäten auf proprietäre und undurchsichtige Weise verwaltet, wodurch Inhalte den Launen von Unternehmensrichtlinien und externem Druck ausgesetzt werden, was zu Überwachung, gezielter Zensur oder einseitiger algorithmischer Manipulation von Inhalten führen kann. Das Design von Nostr - das auf kryptografischer Authentifizierung, clientseitiger Datenaggregation und dem erlaubnisfreien Betrieb von Relay-Servern beruht - stellt eine radikale Abkehr dar, die das Gleichgewicht der Macht fest in die Hände der einzelnen Nutzer und nicht in die Hände zentraler Behörden legt.
7. Implikationen für Bildungsplattformen
Das Potenzial für die Integration des dezentralen Protokolls von Nostr in Bildungsplattformen bietet eine transformative Gelegenheit zur Unterstützung von Open Educational Practices (OEP). OEP legt den Schwerpunkt auf Inklusion, Autonomie der Lernenden, kollaborative Wissenserstellung und offenen Zugang zu Bildungsressourcen. Herkömmliche Bildungsplattformen sind oft durch zentralisierte Architekturen eingeschränkt, die den Zugang behindern und Innovationen unterdrücken können, da sie auf einzelne administrative Kontrollen und proprietäre Content-Management-Systeme angewiesen sind.
Durch die Nutzung der dezentralen Infrastruktur von Nostr können Bildungsplattformen aufgebaut werden, die es Lehrenden und Lernenden ermöglichen, die volle Kontrolle über ihre digitalen Identitäten und Bildungsinhalte zu behalten, ohne das Risiko von Zensur oder externer Einmischung. In solchen Systemen verwaltet jeder Teilnehmer seine eigene Identität mithilfe von kryptografischen Schlüsseln, wodurch sichergestellt wird, dass Bildungsleistungen, Beiträge und Zeugnisse auf überprüfbare und unveränderliche Weise aufgezeichnet werden. Dies fördert ein Umfeld, in dem die Schaffung und Verbreitung von Wissen wirklich von den Teilnehmern selbst bestimmt wird, frei von den Zwängen, die von zentralen Torwächtern auferlegt werden.
Darüber hinaus bietet die relaisbasierte Architektur von Nostr eine beispiellose Skalierbarkeit und Ausfallsicherheit - Eigenschaften, die für ein Bildungsökosystem, das eine Vielzahl von Nutzern mit unterschiedlichem geografischen und sozioökonomischen Hintergrund unterstützen muss, unerlässlich sind. Bildungsinhalte - von digitalen Lehrbüchern und Multimedia-Vorlesungen bis hin zu interaktiven Diskursen und gemeinschaftlichen Projekten - können gespeichert und über mehrere Relays repliziert werden, um sicherzustellen, dass der Zugang auch bei lokalen Netzwerkausfällen oder Zensurversuchen erhalten bleibt.
Das offene Protokoll von Nostr ist außerdem eine ideale Grundlage für die Entwicklung interoperabler Bildungsplattformen, auf denen Drittentwickler und Bildungseinrichtungen maßgeschneiderte Clients und Anwendungen für pädagogische Zwecke erstellen können. Dieser Ansatz fördert ein vielfältiges Ökosystem von Bildungswerkzeugen und -diensten, die nahtlos zusammenarbeiten, ohne auf eine einzige proprietäre Plattform beschränkt zu sein, und steht damit im Einklang mit dem Ethos des OEP. Pädagogen können digitale Lernumgebungen entwerfen, die die kollaborative Erstellung von Inhalten, Peer-Reviews und Community-gesteuerte Kuration unterstützen und gleichzeitig von der Sicherheit und Transparenz profitieren, die das kryptografische Grundgerüst von Nostr bietet.
Darüber hinaus gewährleistet die inhärente Zensurresistenz von Nostr, dass Bildungsinhalte zugänglich und frei von staatlichen oder unternehmerischen Eingriffen bleiben - ein besonders wichtiger Aspekt für Lernende in Regionen, in denen der Zugang zu Informationen eingeschränkt oder überwacht wird. Diese Widerstandsfähigkeit untermauert nicht nur die demokratische Verbreitung von Wissen, sondern unterstützt auch den Grundsatz eines digitalen Gemeinguts, bei dem Bildungsressourcen kollektiv verwaltet und gemeinsam genutzt werden. In diesem Zusammenhang kann Nostr genutzt werden, um Bildungsplattformen zu entwickeln, die nicht nur robust und integrativ sind, sondern auch auf die Bedürfnisse marginalisierter oder unterrepräsentierter Gemeinschaften abgestimmt sind.
Zusätzlich zu diesen strukturellen Vorteilen kann die finanzielle Nachhaltigkeit dezentraler Bildungsplattformen durch die Integration von auf Kryptowährungen basierenden Anreizmechanismen gestärkt werden - wie die Unterstützung von Nostr für Bitcoin Lightning "Zaps" zeigt. Diese Micropayment-Systeme eröffnen Möglichkeiten für neuartige Finanzierungsmodelle, die Pädagogen und Inhaltsersteller direkt belohnen und so die Abhängigkeit von werbebasierten Einnahmen oder zentralisierten Finanzierungsströmen verringern, die häufig die Integrität der Bildung gefährden. Solche wirtschaftlichen Anreize können auch den Betrieb und die Wartung von Relay-Servern unterstützen und so sicherstellen, dass die dezentrale Infrastruktur belastbar und kontinuierlich für Bildungszwecke verfügbar bleibt.
8. Möglichkeiten für kollaboratives und kultursensibles Lernen
Über die technische Stabilität und Skalierbarkeit hinaus bietet die dezentrale Natur von Nostr bedeutende Möglichkeiten zur Förderung von kollaborativem Lernen und kultursensibler Pädagogik. Dezentralisierte Bildungsplattformen, die auf Nostr aufbauen, können lokale Gemeinschaften in die Lage versetzen, Inhalte zu erstellen und zu kuratieren, die kontextuell relevant und kulturell angemessen sind - ein entscheidender Faktor bei der Förderung von Bildungsgerechtigkeit und Inklusivität. In Umgebungen, in denen Mainstream-Bildungstechnologien als von oben nach unten betrachtet werden und nicht mit lokalen Werten oder pädagogischen Ansätzen übereinstimmen, ermöglicht eine dezentralisierte Infrastruktur die Entwicklung maßgeschneiderter digitaler Lernumgebungen, die lokale Kulturen, Sprachen und Traditionen widerspiegeln.
Dieser gemeinschaftsorientierte Bildungsansatz fördert das Gefühl der Eigenverantwortung bei Lernenden und Lehrenden gleichermaßen und ermutigt zur gemeinschaftlichen Schaffung von Wissen, das unterschiedliche Erkenntnistheorien respektiert. So können Pädagogen beispielsweise dezentrale "Lernräume" einrichten, in denen Open-Source-Lernmaterialien, Werkzeuge für die digitale Kompetenz und innovative Lehrmethoden gemeinsam genutzt und durch partizipatives Engagement kontinuierlich weiterentwickelt werden. In einem solchen Modell verschwimmen die Grenzen zwischen Lernenden und Lehrenden, was einen fließenden Ideenaustausch und die gemeinsame Schaffung von Wissen ermöglicht, die im Mittelpunkt offener Bildungspraktiken stehen.
Darüber hinaus ermöglicht die Flexibilität der Client-zentrierten Architektur von Nostr die Entwicklung von spezialisierten Bildungsclients, die auf die jeweiligen Lernstile und Disziplinen zugeschnitten sind. Diese Clients könnten Funktionen wie erweiterte Such- und Filterfunktionen für Bildungsinhalte, integrierte Anmerkungswerkzeuge für die gemeinsame Bearbeitung von Dokumenten und interoperable Identitätsmanagementsysteme enthalten, die es den Lernenden ermöglichen, ihre Anmeldedaten nahtlos in verschiedene digitale Lernumgebungen zu übertragen. Solche Innovationen würden nicht nur die Rolle der Nutzerautonomie beim digitalen Lernen stärken, sondern auch die Entwicklung von Bildungsnetzwerken fördern, die belastbar und anpassungsfähig sind und auf die sich verändernden pädagogischen Herausforderungen reagieren können.
9. Herausforderungen und Abhilfestrategien
Trotz der vielversprechenden Möglichkeiten ist die Integration von Nostr in Bildungsplattformen nicht unproblematisch. Gerade die Funktionen, die den Nutzern mehr Möglichkeiten bieten - wie selbstverwaltete kryptografische Schlüssel und dezentralisierte Inhaltsmoderation - führen auch Komplexitäten ein, die die Benutzerfreundlichkeit und Zugänglichkeit behindern können, insbesondere für Personen ohne fortgeschrittene technische Kenntnisse. Die Schlüsselverwaltung stellt beispielsweise eine kritische Schwachstelle dar; der Verlust eines privaten Schlüssels führt unwiderruflich zum Verlust der Identität und des Zugriffs auf die eigenen digitalen Beiträge - ein Risiko, das durch solide Bildungsinitiativen und Mechanismen zur Unterstützung der Nutzer angegangen werden muss.
Die technische Kompetenz von Lehrenden und Lernenden ist in diesem Zusammenhang von größter Bedeutung und erfordert die Entwicklung umfassender Einführungsverfahren, benutzerfreundlicher Schnittstellen und Hilfsmittel, die kryptografische Konzepte entmystifizieren und die Interaktion mit dezentralen Netzwerken vereinfachen. Zu diesem Zweck könnte der Einsatz intuitiver Bildungsmodule, interaktiver Tutorials und von der Community geleiteter Schulungen technische Barrieren abbauen und gleichzeitig die Entwicklung digitaler Kompetenzen fördern, die für die Navigation in dezentralen Netzwerken unerlässlich sind. Darüber hinaus muss die Herausforderung einer inkonsistenten Moderation und fragmentierten Nutzererfahrung aufgrund der heterogenen Richtlinien unabhängiger Relais und Clients durch die Einrichtung von Community-Governance-Rahmenwerken und interoperablen Standards angegangen werden, die eine Grundlinie der Qualität und Sicherheit auf der gesamten Plattform gewährleisten.
Strategien zur Bewältigung des mit der Skalierbarkeit verbundenen Overheads - wie etwa die redundante Replikation von Beiträgen über eine übermäßige Anzahl von Relays - sollten sich auf die Implementierung clientseitiger Optimierungstechniken konzentrieren, die die Ineffizienz von Bandbreite und Speicherplatz verringern, ohne die Belastbarkeit und Zugänglichkeit des Netzwerks zu beeinträchtigen. Kontinuierliche Forschung und iterative Verfeinerung werden notwendig sein, um ein Gleichgewicht zwischen den Vorteilen der Dezentralisierung und der ihr innewohnenden betrieblichen Komplexität zu finden und sicherzustellen, dass auf Nostr basierende Bildungsplattformen sowohl robust als auch benutzerfreundlich bleiben können.
10. Zukünftige Richtungen und Forschungsmöglichkeiten
Die Einbindung von Nostr in Bildungsplattformen stellt ein fruchtbares Gebiet für Forschung und Entwicklung dar, das zahlreiche Möglichkeiten zur Erkundung bietet. Zukünftige Arbeiten könnten das Design interoperabler Bildungsrahmenwerke erforschen, die die dezentrale Architektur von Nostr mit aufkommenden Technologien wie künstlicher Intelligenz, Blockchain-basiertem Credentialing und fortschrittlichen kryptographischen Techniken integrieren, um die Sicherheit, Zugänglichkeit und Authentizität in digitalen Lernumgebungen weiter zu verbessern. Die Erforschung gemeinschaftsbasierter Governance-Modelle ist ebenfalls gerechtfertigt, da dezentrale Plattformen Mechanismen für die kollektive Entscheidungsfindung und Konfliktlösung erfordern, die mit den Grundsätzen einer offenen, partizipativen Bildung vereinbar sind.
Ein möglicher Weg ist die Entwicklung modularer, quelloffener Bildungs-Clients, die sich nahtlos mit verschiedenen Relais verbinden lassen und den Lehrkräften leistungsstarke Tools zur Kuratierung und Moderation von Inhalten bieten. Diese Clients könnten anpassbare Dashboards, Module für die Zusammenarbeit in Echtzeit und integrierte Unterstützung für Mikrozahlungen oder Anreizstrukturen bieten, um sicherzustellen, dass Bildungsinhalte sowohl dynamisch als auch finanziell nachhaltig bleiben. Darüber hinaus könnte die Einrichtung digitaler Identitätsrahmen, die auf den kryptografischen Prinzipien von Nostr aufbauen, zu innovativen Modellen für die Überprüfung akademischer Zeugnisse, die Verfolgung des Lernfortschritts und die Erleichterung der plattformübergreifenden Anerkennung von Bildungsleistungen führen, und das alles ohne die Aufsicht zentralisierter Registrierungsbehörden.
Die Schnittstelle zwischen digitaler Kompetenz und ethischer digitaler Bürgerschaft ist ein weiteres vielversprechendes Forschungsgebiet. In dem Maße, in dem Pädagogen dezentrale Bildungstechnologien in die Lehrpläne integrieren, wird es zwingend notwendig, Lehrmethoden zu entwickeln, die nicht nur technische Kenntnisse, sondern auch die kritischen und moralischen Fähigkeiten vermitteln, die für die Arbeit in einem dezentralen digitalen Ökosystem erforderlich sind. Solche pädagogischen Strategien sollten Schulungen zum Schlüsselmanagement, zur Verifizierung digitaler Identitäten und zum Verständnis der Kompromisse umfassen, die mit dezentralisierten und zentralisierten Technologiemodellen einhergehen, um den Schülern eine ausgewogene Perspektive auf digitale Rechte, Verantwortlichkeiten und Möglichkeiten zu vermitteln.
Die Zusammenarbeit zwischen akademischen Institutionen, Open-Source-Gemeinschaften und Innovatoren dezentraler Technologien wird entscheidend sein, um diese Forschungsagenden voranzutreiben und die Entwicklung von Bildungslabors und Pilotprojekten zu fördern, die die praktischen Auswirkungen und Vorteile dezentraler Bildungsplattformen auf der Grundlage von Nostr erforschen. Solche Initiativen könnten als lebende Laboratorien zum Testen neuer Werkzeuge, Methoden und Governance-Strategien dienen, mit dem Ziel, das Gleichgewicht zwischen dem Versprechen der Dezentralisierung und ihren praktischen Herausforderungen schrittweise zu verfeinern.
11. Schlußfolgerung
Zusammenfassend lässt sich sagen, dass Nostr eine bahnbrechende Entwicklung in der Architektur sozialer Medien darstellt, die die Beziehung zwischen Nutzern, Inhalten und Netzwerkinfrastruktur durch ein dezentralisiertes, kryptographisch gesichertes und klientenzentriertes Modell neu definiert. Das relaisbasierte Design, die dezentrale Identitätsverwaltung und die offene Architektur bieten erhebliche Vorteile gegenüber herkömmlichen zentralisierten und föderierten Systemen in Bezug auf Zensurresistenz, Skalierbarkeit und Benutzerautonomie. Diese technischen Innovationen haben weitreichende Auswirkungen auf die Entwicklung von Bildungsplattformen, die den Grundsätzen der Open Educational Practices entsprechen. Durch die Unterstützung von nutzergesteuerten Identitäten, stabiler Replikation von Inhalten und gemeinschaftsgesteuerter Verwaltung bietet Nostr eine Infrastruktur für dezentrale Bildungsökosysteme, die Inklusion, Zusammenarbeit und kontinuierliche Innovation fördern.
Der Einsatz von Nostr in Bildungskontexten verspricht, Lernende und Lehrende in die Lage zu versetzen, Bildungsinhalte frei von zentralisierten Einschränkungen und externer Zensur zu erstellen, zu teilen und gemeinschaftlich weiterzuentwickeln. Gleichzeitig erfordern die Herausforderungen, die mit der technischen Komplexität, der Schlüsselverwaltung und der inkonsistenten Moderation verbunden sind, kontinuierliche Forschung und die Entwicklung unterstützender Werkzeuge. Wenn diese Probleme durch gezielte Maßnahmen wie benutzerfreundliche Schnittstellen, umfassende Programme für digitale Kompetenz und gemeinschaftsbasierte Governance-Modelle angegangen werden, können die Beteiligten das volle Potenzial von Nostr nutzen, um dezentrale, offene und partizipative Bildungsplattformen zu schaffen, die den Geist von Open Educational Practices wirklich verkörpern.
Letztendlich stellt die Integration von Nostr in dezentralisierte Bildungsplattformen nicht nur eine technische Entwicklung dar, sondern auch einen gesellschaftspolitischen Wandel hin zu größerer Dezentralisierung, Ermächtigung der Nutzer und digitaler Souveränität. Diese Ausrichtung an den Werten des OEP definiert nicht nur die Verbreitung und den Konsum von Bildungsinhalten neu, sondern ist auch Katalysator für breitere Diskussionen über digitale Rechte, Inklusion und ethische Teilhabe an der digitalen Allmende. Das Potenzial solcher Plattformen, kontextrelevante, zensurresistente und kollaborativ kuratierte Bildungsressourcen bereitzustellen, ist ein entscheidender Schritt, um die Zukunft der digitalen Bildung neu zu gestalten.
Fazit
Zusammenfassend lässt sich sagen, dass die innovative Architektur von Nostr, die auf einer kryptografischen Schlüsselverwaltung und dezentralen Relay-Netzwerken basiert, den Grundstein für eine neue Generation von Bildungsplattformen legt, die die Einschränkungen zentralisierter Systeme überwinden können. Ihre Fähigkeit, belastbare, sichere und nutzerzentrierte digitale Umgebungen bereitzustellen, steht in perfektem Einklang mit den Grundsätzen offener Bildungspraktiken und bietet Lehrenden und Lernenden eine noch nie dagewesene Kontrolle über ihre digitalen Interaktionen und Inhalte. Kontinuierliche Forschung, interdisziplinäre Zusammenarbeit und gezielte Bildungsinitiativen werden unerlässlich sein, um dieses Potenzial voll auszuschöpfen und sicherzustellen, dass die Vorteile der Dezentralisierung allen Mitgliedern der Bildungsgemeinschaft zugänglich sind.
Durch den strategischen Einsatz von Nostr-basierten Bildungsplattformen kann die Zukunft des Lernens als ein Bereich neu konzipiert werden, in dem offener Zugang, Autonomie der Lernenden und gemeinschaftsgesteuerte Wissensbildung nicht nur möglich, sondern unvermeidlich sind - eine Zukunft, in der dezentrale Infrastrukturen eine gerechtere, transparentere und partizipativere digitale Bildungslandschaft ermöglichen.
Dieser Beitrag hat daher eine ausführliche Einführung in die technischen und konzeptionellen Grundlagen von Nostr gegeben, die Mechanismen beschrieben, mit denen Nostr Dezentralisierung und Zensurresistenz erreicht, und seine bedeutenden Auswirkungen auf die Zukunft von Bildungsplattformen im Rahmen von Open Educational Practices untersucht. Die Synergie zwischen dem dezentralen Paradigma von Nostr und dem demokratischen, inklusiven Ethos von OEP birgt ein transformatives Versprechen für die Neugestaltung der digitalen Bildung in einer Weise, die Offenheit, Sicherheit und lebenslanges Lernen für eine globale Gemeinschaft fördert.
Indem sie aufkommende dezentralisierte Protokolle wie Nostr als grundlegende Infrastrukturkomponenten von Bildungsplattformen nutzen, können Stakeholder eine ganzheitliche digitale Transformation vorantreiben, die Technologie, Pädagogik und Ethik vereint und ein Paradigma einführt, in dem Bildungsgerechtigkeit und digitale Selbstbestimmung keine Wünsche, sondern realisierte Prinzipien unserer vernetzten Gesellschaft sind.
Verwendete Quellen:
-
Seeing the Politics of Decentralized Social Media Protocols. S Hwang, AX Zhang. ArXiv (2025). <https://doi.org/10.48550/arxiv.2505.22962>
-
Navigating Decentralized Online Social Networks: An Overview of Technical and Societal Challenges in Architectural Choices. Ujun Jeong, L. Ng, K. Carley, Huan Liu. ArXiv (2504). <https://doi.org/10.48550/arxiv.2504.00071>
-
Towards Decentralized Applications. X Ma. 2024. <https://escholarship.org/content/qt0j7044w0/qt0j7044w0_noSplash_c638cdfda170244b9abf750f654399f1.pdf>
-
Decentralized Social Networking Protocol (DSNP) and User Empowerment: An Analysis of Online Identity Ownership, Data Privacy, and Comparative Assessment with Other Decentralized Protocols. M Nay . 2024. <https://dspace.mit.edu/bitstream/handle/1721.1/156782/nay-mnay-meng-eecs-2024-thesis.pdf?sequence=1&isAllowed=y>
-
A Kantian Right to Fediverse Access, or: for a digital enlightenment on the social web. JN Bingemann . <https://philarchive.org/archive/BINAKR>
-
Exploring the Nostr Ecosystem: A Study of Decentralization and Resilience. Yiluo Wei, Gareth Tyson. ArXiv (2402). <https://doi.org/10.48550/arxiv.2402.05709>
-
Money and Trust in Metaverses, Bitcoin and Stablecoins in global social XR. John O'Hare, Allen J. Fairchild, U. Ali. ArXiv (2207). <https://doi.org/10.48550/arxiv.2207.09460>
-
FEDSTR: Money-In AI-Out | A Decentralized Marketplace for Federated Learning and LLM Training on the NOSTR Protocol. Konstantinos E. Nikolakakis, George Chantzialexiou, Dionysis Kalogerias. ArXiv (2024). <https://doi.org/10.48550/arxiv.2404.15834>
-
"Sumud" as Connected Learning: Towards a Collective Digital Commons in Palestine.. H Scott, M Ujvari, AMA Bakeer. 2025. <https://files.eric.ed.gov/fulltext/EJ1464483.pdf>
Erstellt mit Unterstützung von FutureHouse, Perplexity, Deepl, Ideogram und ChatGPT.
-
-
 @ da8b7de1:c0164aee
2025-06-04 16:37:07
@ da8b7de1:c0164aee
2025-06-04 16:37:07Nukleáris politika és szabályozási fejlemények
A Nemzetközi Atomenergia-ügynökség (IAEA) Kormányzótanácsa 2025. június 9-én kezdi meg szokásos júniusi ülését Bécsben. A főbb napirendi pontok között szerepel a 2024-es éves jelentés, a technikai együttműködési tevékenységek, az iráni ellenőrzés és felügyelet, az ellenőrzések végrehajtása Észak-Koreában és Szíriában, a nukleáris biztonság és védelem Ukrajnában, valamint a nukleáris anyagok átruházása és ellenőrzése az AUKUS-keretében. Az ülésen új tagokat is kijelölnek a Kormányzótanácsba, és előkészítik a 69. rendes közgyűlést[iaea.org].
Jelentős projektek és iparági bővülés
Az amerikai Tennessee Valley Authority (TVA) benyújtotta kérelmét az Egyesült Államok Nukleáris Szabályozási Bizottságához egy GE Vernova Hitachi BWRX-300 kis moduláris reaktor (SMR) megépítésére a Clinch River telephelyen, ami jelentős lépés az amerikai fejlett nukleáris technológiák elterjesztésében[world-nuclear-news.org]. Kanadában a hatóság engedélyezte az Ontario Power Generation számára, hogy egy BWRX-300 reaktort építsen a Darlington New Nuclear Project helyszínen, ezzel tovább haladva az észak-amerikai SMR-projektek terén[world-nuclear-news.org].
India nukleáris szabályozója jóváhagyta a négyblokkos Mahi Banswara Rajasthan Atomerőmű telephelyét, Kínában pedig folytatódnak a szerelési munkák a Haiyang 3 egységen. Eközben Belgium és Dánia felülvizsgálják nukleáris politikájukat: Belgium visszavonja a korábbi leállítási döntést, Dánia pedig újragondolja álláspontját[world-nuclear-news.org].
Ellátási lánc, munkaerő és nemzetközi együttműködés
A nukleáris kapacitás várható gyors növekedése miatt egyre nagyobb hangsúly kerül mind a helyi, mind a globális ellátási lánc felkészítésére. A World Nuclear Association legutóbbi konferenciája kiemelte az ellátási lánc „globalizációjának” fontosságát a bővülés támogatásához[world-nuclear-news.org]. A nukleáris munkaerő világszerte növekedni fog, ami új lehetőségeket teremt, nem pedig hiányt. Az iparági szakértők hangsúlyozzák a jelentkezők tapasztalatának javítását és a szektorok közötti készségek hasznosítását a jövőbeni igények kielégítésére[world-nuclear-news.org].
A nemzetközi szabályozói együttműködés is fejlődik, különösen a kis moduláris reaktorok (SMR) tervezési értékelése terén. A brit Nukleáris Szabályozási Hivatal közzétette első jelentését ebben a témában, globális szinten hatékonyabb és összehangoltabb megközelítést célozva[world-nuclear-news.org].
Gazdasági és befektetési trendek
A nukleáris szektorban újra optimizmus tapasztalható, egészséges projektportfóliókkal és növekvő magánbefektetésekkel, különösen a fejlett üzemanyagok, például a HALEU (magas dúsítású urán) terén. A Világbank lehetséges politikai váltása, amely lehetővé tenné nukleáris projektek finanszírozását, jelentős hatással lehet a globális befektetésekre, példát mutatva más hitelezőknek is[ans.org].
Az USA-ban jelentős lépés a Prohibiting Russian Uranium Imports Act életbe lépése, amely megtiltja a feldolgozatlan, alacsony dúsítású orosz urán behozatalát, és 2,72 milliárd dollár szövetségi támogatást szabadít fel a hazai urántermelés fellendítésére. A törvény 2027-ig korlátozott mentességeket engedélyez, 2040-ben pedig lejár[ans.org].
Technológia és innováció
A TerraPower hivatalosan is jelezte a brit hatóságoknak, hogy megkezdi a Natrium nátrium-hűtésű gyorsreaktor általános tervezési engedélyezési folyamatát, ezzel jelezve, hogy a vállalat nemzetközi szinten is be kívánja vezetni ezt a technológiát[world-nuclear-news.org]. Olaszországban új nemzeti bizottság alakult a radioaktív anyagok szállításával kapcsolatos kihívások kezelésére, a megfelelőség és a logisztika egyszerűsítése érdekében[world-nuclear-news.org].
Az Enel, az Ansaldo Energia és a Leonardo megalapította a Nuclitalia céget, hogy tanulmányozza a fejlett nukleáris technológiákat és elemezze a piaci lehetőségeket, ami jól mutatja az európai érdeklődés növekedését a következő generációs nukleáris megoldások iránt[world-nuclear-news.org].
Friss és közelgő események
- Az IAEA Kormányzótanácsának ülése (2025. június 9–13.) számos politikai, biztonsági és védelmi kérdéssel foglalkozik majd[iaea.org].
- Az amerikai Fehér Ház nemrégiben csúcstalálkozót tartott a hazai nukleáris fejlesztésekről, és elindította a legnagyobb szövetségi kezdeményezést az elmúlt ötven évben a hálózati méretű nukleáris reaktorok felgyorsított építésére[ans.org].
Források: - world-nuclear-news.org - iaea.org - ans.org - nucnet.org
-
 @ 1ef61805:f18312cc
2025-06-04 01:56:42
@ 1ef61805:f18312cc
2025-06-04 01:56:42**Inside OpSec Academy’s One-on-One Approach to Digital Sovereignty ** As digital infrastructure becomes increasingly opaque and centralised, a growing number of individuals are seeking to understand—not just use—the tools that protect their privacy and autonomy online. While many solutions promise security at the click of a button, few teach the underlying principles or offer environments that prioritise verifiability and user control.
OpSec Academy’s new one-on-one training, "OpSec Intensive," takes a different approach. Delivered in person and fully offline, the full-day session provides practical, tool-based instruction inside a secure, USB-booted environment—designed from the ground up to leave no trace.
At the heart of the session is OpSecOS v1.2, a live operating system that routes all traffic through Tor, uses system non-persistence, and comes preconfigured with a suite of open-source tools for password management, communication, and private finance. The OS runs from a USB stick, allowing participants to explore and build their own private computing workflows without touching the host machine.
Learning in Context: Why One-on-One? While group training can provide a general introduction to privacy concepts, it often lacks depth and adaptability. OpSec Intensive is structured as a one-on-one session to allow real-time feedback, personal threat modeling, and tailored instruction based on the participant’s specific context and technical background.
This format also makes space for slow, deliberate learning—a rarity in cybersecurity training, where content is often condensed or overly abstract. In OpSec Intensive, participants move through each phase at their own pace, working directly with an experienced instructor to build confidence and competence.
Structure and Content of the Day The curriculum spans both foundational theory and hands-on practice, beginning with basic OpSec principles before moving into technical tool use.
Topics include: * Booting and verifying OpSecOS * Secure USB creation and system verification * Navigating a non-persistent, Tor-routed live environment * Password and credential management * Offline use of KeePassXC * Strategies for vault organisation and redundancy * Bitcoin wallet setup and recovery * Single-signature and multisignature wallet creation using Sparrow, Electrum, and Feather * Understanding xpubs, derivation paths, and recovery flow * Seed phrase security * Entropy generation and validation using offline tools like iancoleman.io * Best practices for cold storage and physical backups * Network privacy and decentralised communication * Using Mempool.space to visualise Bitcoin transaction data * Setting up Nostr clients (Snort, Iris) for decentralised messaging * Discussion of traffic fingerprinting and Tor considerations
A Shift Toward Practical Sovereignty The tools and workflows covered in OpSec Intensive are not theoretical. Participants leave the session with configured environments, tested backups, and an understanding of what each tool does—and what it doesn’t do.
This reflects a broader shift in how privacy-conscious individuals are approaching digital security. Rather than relying on packaged services or closed-source software, there’s growing interest in verifiable, modular tools that prioritise autonomy and resilience over ease-of-use.
In that context, OpSec Academy’s offering sits somewhere between a workshop and an apprenticeship: not a lecture, but a process of guided, hands-on learning designed for the long haul.
To learn more or enquire about availability, visit opsecacademy.org.
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 5188521b:008eb518
2025-06-03 12:25:39
@ 5188521b:008eb518
2025-06-03 12:25:39Elysium
Part I: The Failed Harvest
First, the quiet came. Each day, the markets grew quieter, the people hungrier. A farmer stared at wilted crops, dread settling in his heart. In a kingdom once resplendent with markets and sky-reaching monuments, it was the first failed harvest that marked the end of affluence and the beginning of collapse.
By the second year, market traders stood before empty stalls, goods long gone, rotten, or ruined. Jobless men prowled, foraging the streets for vermin and meager scraps of sustenance. Young women offered their time for bread, their eyes hollow in the act. Widows, too, entered strangers’ homes, bartering themselves for their children’s next meal. Orphans, gaunt and brittle, drew meaningless shapes in the dust, their laughter a forgotten memory.
Rumors surged like wind through dry grass. Scapegoats were blamed; superstitions gripped the masses. By the third year, it was known to the people and the king alike, there would be no more monuments erected, only tombstones. The king called the council, heavy with despair. In a room filled with tension, ministers and knights sat around a table.
Before them stood the realm’s wisest farmer, a man worn from years of labor, hunger, and loss. His voice echoed the deep hunger that gripped the kingdom. “Your Majesty, the land is weary. It cries for respite.” His words hung heavy in the room, laying bare the reality of their fate.
Part II: The Devil’s Pact
In the dimly lit chamber, a palpable tension filled the air. The alchemist, servant to the king and master of arcane arts, stepped into the flickering candlelight. He held an aged book, its scent mingling with the murk of looming spells. With a voice both smooth and haunting, he shattered the quiet, his words a ripple through stone walls.
“Sire, alchemy is our last refuge. We can harvest time to feed the earth,” he began, revealing a parchment inked with cryptic circles and lines. “Each citizen, willingly or not, will spare a mere whisper of their years. An unnoticeable offering. With careful alchemy, we can replenish our lands and fortify your reign with the alms of myriad souls.” Leaning closer, he whispered the words that would redefine their civilization: a devil’s proposal intended for the king but felt by all. “Consider, my lord, a reign without end, each year stretched beyond nature’s limits, a kingdom fed by the borrowed time of its people. No more famine. No more want.”
The court waited, their faces etched with fear and desperate hope, ready to tread any path that led away from the abyss of famine.
For a moment, the king was a statue, his face a veil behind which storms brewed. Finally, exhaling a breath heavy with fate, he spoke. “We’ve endured enough hardship. We shall seize a future that knows no famine.”
The air thickened as the alchemist retreated with a solemn nod, the weight of the chosen path settling in.
He reopened his tome and voiced the incantation. Arcane syllables filled the room, weaving a desperate gambit to salvage their decaying kingdom. Thus, in the dark hours of night, they sealed a new covenant that would reverberate through generations.
Part III: Vines and Moss
In the decades that followed the alchemist’s rites, the kingdom thrived like spring after a bitter winter. Fields were lush year-round, erasing hunger and the memories of famine. Marketplaces bustled, no longer a graveyard of commerce but a carnival of exotic goods from every corner of the world. The air seemed perfumed with prosperity — healthy river fish, basilisk meats, and spices from faraway lands. A century rolled by. The king, unaging, stretched his influence over land and sea, turning his realm into an empire. Statues weathered, and languages evolved, but the king abided.
Yet, a toll was exacted. Years stolen from the people, a time tax woven into the fabric of life. The spell fed both earth and crown, cloaking decay with a veneer of wealth. The young wore the faces of old men, their eyes wise beyond their years. Every heartbeat was a sacrifice, a quiet tax to feed the castles of power.
Then came the year when the land rebelled. Coaxed by the spell, the soil had given until it couldn’t, its silent plea for rest ignored. The land remembered stolen seasons, now determined to settle old scores. Crops withered; rivers soured. Beasts waned, their numbers thinning. The kingdom, starved of Earth’s gifts, unraveled — not from human revolt, but from the silent insurrection of the land that once fed them.
With hunger as the harbinger, society fractured. Chaos and mass confusion swallowed the land, a virulent blight not even alchemy could stem. Witch hunts raged for a merciless century, fire consuming flesh and innocence. Men’s strength wilted, armies disbanded. Women, walking in the agonizing footsteps of famine-haunted foremothers, bartered touch for bread.
Monuments lay buried under vines and moss. Fertile lands turned barren. Schools emptied, their echoing halls abandoned, and children torn from learning, were sent to farm dying lands. Art withered. Painters swapped colors for shades of gray, and soon vanished altogether. Teachers and engineers were supplanted by an ever-growing class of soil-bound serfs.
Desperate, the eternal king sought another spell. He asked the people not for mere years but decades. The alchemist obliged, crafting another spell from dark incantations. Yet the ravaged earth, too spent to yield, exacted a monstrous price: lifetimes for crumbs of bread. People, skeletal, on the verge of vanishing, offered their very existence. A silence settled, a collective sacrifice borne not in rebellion, but in surrender.
Part IV: Clara The Torchbearer
In the land between sleep and waking, Clara was a child again, standing at the threshold of a room aglow with amber light. Her mother ground herbs, the wooden table before her strewn with books, vials, and leaves. “These aren’t just leaves and liquids,” her mother said. “They’re doors to the gardens of your mind.” Her words sank into Clara like stones into deep water.
She woke to a gusting wind. Her dream dissolved like morning mist. The sun broke over the kingdom, time’s toll evident in every vine-entangled ruin. Light spilled into her chamber.
Clara’s room was modest: a bed, a wardrobe, a desk. On it, a lone candle and scattered books that whispered of the kingdom’s past grandeur and freedoms now lost. It was her mother’s notes and books, crafted in the quiet, away from royal eyes — a puzzle to decipher, a quest still yearning for footsteps.
She draped a linen robe over her shoulders and approached the window, her fingers ink-stained from yesterday’s writings. Below, people shuffled through life, joyless and muted.
The spell cast long ago had become an oppressive, faceless dictator. It promised bread but dealt only crumbs, a tarnished magic now woven into the kingdom’s culture as enduringly as its ancient stone walls and teeming graveyards.
She remembered the cold spring day she put her mother in the earth. The ground was hard, the casket simple. The tombstone bore the words: ‘Seed in Drought.’
The chambermaid standing beside her asked what it meant.
“Her wish,” Clara answered. Her face gave nothing away, her thoughts a distant country.
From her room, Clara watched the people below — eyes down, spirits broken. Clara was not like the others. She carried an inner fire, gifted from her mother, a quiet revolt against a gray world.
In her room’s sanctuary, amid ink and parchment molded by hands long stilled, Clara found traces of a freer past, free from famine and theft of years. A past now entrusted to her. As she flipped through the timeworn pages of an ancient tome, something caught Clara’s eye. In the margins of the text, a note penned in her mother’s hand: “For Clara — Elric is the keeper of truths that free us. Go where I could not. Find him.” Below it, a tender signature, her mother’s name etched in ink.
The name ‘Elric’ stirred a latent memory, a shared secret often spoken by her mother. Filled with a sense of destiny, Clara closed her worn books and left her chamber.
At the age of twenty, for the first time, she ventured beyond the confining walls of her castle. Guided by remnants of forgotten eras, she set forth to unearth truths long interred but never wholly erased. Her compass drew her toward the Whispering Pines, a land untouched by the alchemist’s dark arts and, as her mother had often mentioned, the rumored dwelling of Elric.
Part V: Far to Go
Clara walked through towns void of kindness, over land stripped of life. Each day sculpted her in the likeness of the land she traversed — a leaner body, hands hardened, face etched by sun and wind.
Thirteen days out, Clara trudged through the ashen remains of a town, its name forgotten, its history lost. Empty buildings sagged under the weight of time, their hollow frames like gravestones against the evening sky. Vacant faces, like clock dials without hands, glanced through her, never at her.
Spying a run-down tavern, she cautiously stepped inside. The door whined on rusted hinges. She eased onto a splintered stool. “Bread,” she rasped. The innkeeper, a bloated man with eyes like rotted plums, flung stale crust onto the counter. Her teeth sank into the stale crust, her body weeping for nourishment.
The room stank of unwashed bodies and sour ale. In a dim corner, men gambled their souls on dice, their faces marred by desperation and greed. As she made to leave, talk stilled, and eyes tracked her. A rough hand seized her wrist.
“Far to go?” The words, a mockery.
Her eyes darted to the innkeeper, pleading for an ally. His gaze, cold, turned away. “Yes, far,” she replied, stalling.
Then, violence. Teeth, nails, a taste of blood. Outmanned, her screams died in cruel laughter. Her clothes yielded, torn in the contest of her humiliation.
After the degradation, she stepped outside and into the soft rain of the night. Her path now carried weight measured in more than miles.
Ahead, barren land stretched mercilessly. A fleeting image of her mother’s face offered a brief moment of comfort. She tilted her head back, letting rain droplets fall onto her tongue to dilute the bitterness that swelled within her. The night urged in tones only darkness knows. Turn back, it murmured.
But she walked on. Her will was a defiant ember, the last flicker of light in a world teetering on oblivion, its humanity long forfeited.
Part VI: Elric
After weeks traversing a harsh expanse, gaunt but unbroken, she found herself beneath the Whispering Pines. As she approached, she carried more than her own weight. She embodied her mother’s enduring hope and her land’s final prayer for redemption.
Elric greeted her at the doorway. “You’ve come,” he said, leading her inside, the room warm from the fire in the stone hearth.
Her eyes roved from the firelight dancing on the walls to the shelves laden with books. A staircase twisted upward, its banister engraved with ancient symbols.
“Your homeland withers,” Elric said, drawing from his pipe, the wood old and marked by years. The scent of herbs, a blend cultivated through many seasons, sharpened the mind as it filled the room. “The spell,” she confirmed.
“Mmm,” he exhaled, his eyes shifting to the fireplace, wood popping in the heat. “Your forebears knew better days. Days without sacrifice.”
“The legends spoke truth, then?”
“Indeed.”
“Did you know I was coming?”
“I’ve waited twenty years. This isn’t our first meeting.”
“We’ve met before?”
“Once, when you were but a newborn. Your mother and I collaborated. We worked on a potion that siphons the power of nature to protect the truth in our world, to shield it from alchemy and dark spells.”
Elric opened a small cabinet beside the hearth. From it, he took an empty wooden chalice and a stoppered glass vial. Uncorking the vial, he poured a golden liquid into the chalice, the firelight making it shimmer. “This elixir hails from untarnished lands, free from the alchemy that poisons your realm. One sip and illusions shatter, transforming soul and society alike.” “What is it called?” she asked.
He looked at her intently. “Elysium,” he said, the word hanging heavy in the room. “It’s both the end and the beginning of your journey. You must experience it to understand. Drink.”
She sipped the brew; it tasted of nothing. Soon, as she nestled by the fire, the walls took a breath, and the world sharpened as if coming into focus for the first time. The air thickened into a heavy mist, her fingers danced through it, each ripple sending colors splashing around like bioluminescent whispers. She floated, her body dissolving, her name a distant echo.
Elric’s gaze turned to the fire, shadows playing across his face. “Elysium shows only what one needs to see, no more, no less,” he said, his voice a gentle wave against the shores of her uncertainty. “In my own experience with Elysium, I saw a torchbearer in the veil of time, a young soul with the spark to undo the dark spell on your land.” His eyes found Clara’s. “But the torchbearer had to come to me, the journey forging the resolve. Had I sought you out sooner, before your heart was ready, Elysium’s truth would have been a burden too heavy.”
As the reality of his words sank in, Clara felt the weight of the years, the faces of the countless lives lost to the alchemist’s dark magic flashing before her eyes. “And the elixir… why not share it sooner?”
Elric sighed, his eyes drifting to the ancient books lining the shelves. “Elysium’s truth is a double-edged blade. In the wrong hands, it could cut through the fabric of reality, leaving wounds that might never heal. Your kingdom…” he gestured vaguely towards the window, “…it wasn’t ready. But now, the ground has been furrowed by suffering, ready to receive the truth about the universe, the spell, the suffering.”
The walls breathed with a rhythm older than time. She looked at her hands moving through the bioluminescent mist, each movement sending ripples across the room. Tendrils of light danced in the air, ethereal spirits beckoning her towards another realm.
“But why?” Clara pressed, her presence deepening with each breath. “Why involve yourself?”
Elric’s eyes softened. “I once lived in your kingdom, fleeing when I realized the spell’s plague. Your mother and I, we shared a vision of a world free from dark alchemy. But more than a promise to an old friend, it’s a battle against the grasp of evil spells, a grasp threatening to choke the essence of life and freedom from this world. It’s a battle,” he looked at Clara with a profound earnestness, “that now passes to you.”
Suddenly, reality shattered, and her soul twisted and warped through a portal faster and faster until she touched the core of the cosmos.
Here, in a land beyond words, beyond the confines of time and space, she witnessed the birth and demise of the universe. With each breath, a star was born and died; each blink saw the rise and fall of civilizations. Like a photon racing at light speed through the cosmos, untouched by time, she beheld the entirety of all that ever was and will be.
Peering beyond the infinitely small, she saw the source code of the universe, equations as living tendrils of light materializing into particles, planets, and stars. The universe, a symphony of mathematical elegance, its physicality a melody resonating along the strings of her consciousness.
She floated amidst the cosmic code, orchestrating the universe — the planets, the voids, the unseen forces weaving through them — and she was one with all. She was the universe gazing at itself. Beyond the veil of mortality, she saw endless realms, death a mere doorway. In that boundless expanse, she brushed against the face of the divine.
A golden phoenix took form before her.
“I am Veritas,” it spoke, not in words, but in a language of complex geometry.
It exposed the grim truths of her lands, the Great Famine, and the enslaving spell — a counterfeit prosperity bought at the terrible price of human years.
“How do we break free?” Clara’s voice carried the untold suffering of generations.
“Simple,” the phoenix intoned. “Don’t battle the alchemist or his spell; you won’t win. Acknowledge the illusion. Tend to your own gardens, and reliance on the alchemist and the king fades. Elysium shields you, body and mind, from the spell’s reach.”
As the vision faded, Clara found herself back on the wooden floor, her head cushioned by a pillow. The urgency of her quest snapped her back to reality, a newfound resolve kindling in her chest.
“I see now,” she breathed, her voice steady. “I know what I must do.”
Elric nodded, a sage with a deep understanding of the paths of the universe. “Yes, but first, tea. There’s strength to regain and you have a long journey ahead,” he said, anchoring them both in a moment of calm before the impending storm of change.
Part VII: The Wayfarer’s Hearth
After days navigating barren expanses, Clara entered a cobblestone town as twilight settled. Figures lined the street, some alive, some not, most in limbo — too tired to beg, too frail to feed. Candlelight flickered from the windows of a tavern, illuminating well-fed faces. “The Wayfarer’s Hearth,” read the sign above the door.
She approached. The door creaked open to admit her, wafting out stale beer and the scent of roast meat. Her fingers twitched involuntarily, memories of weeks ago crawling up her spine, but her body ached for sustenance, for warmth. Holding her satchel close, safeguarding the vial of Elysium, she chose a chair at an empty table and settled in. Soon enough, food appeared.
The man who had set her meal before her took the adjacent seat with deliberate ease, his eyes lingering on her satchel. Her pulse quickened.
“You carry a weight, wanderer,” he said.
“Or hope,” she countered, her grip on her satchel unyielding.
A glass shattered. Drunkards stumbled into their table, a wave of mead sweeping over worn wood. Clara’s heart surged, the man’s fingers brushed her satchel, pulling the vial from its sanctuary. “Hope carries its own burden,” he said.
“The hope of my people is in that vial,” she shot back, her voice stripped bare.
“This is Elysium,” he said, his words like barbs. “At what cost, wanderer, do you think Elysium will save your people?”
Doubt snaked around her convictions. Was she the bearer of emancipation or a harbinger of calamity? Was her land ready for Elysium? “You know it?” she asked.
“I know it,” he said, eyeing it closely.
“Return it,” she commanded.
He handed over the vial. “The road to freedom is paved with the stones of responsibility. I wouldn’t want to walk in your shoes.”
She nodded, heavy but resolute. Clara left as quietly as she’d come, meal untouched, mission intact.
The night took her in. She cast a final glance back at a room oblivious to her departure. That night, she’d sleep under indifferent stars, closer to home but adrift in certainty, carrying the weight of a thousand stones of untold responsibility, a Trojan’s shroud for her people, a destiny unasked.
Part VIII: This is Elysium
Under a storm-heavy sky, Clara returned home. In her pocket was Elysium; in her mind, a plan that required Harold — an old friend and a knight by trade.
In the guild hall, Harold sat among knights and minstrels, a goblet in hand. “Look at this,” Clara said, pushing the vial across the table without ceremony. Her words pierced the tavern’s noise as she recounted her journey.
Harold looked at her, then at the vial. “You mean to say that one day, this will help us fight the spell?”
“No,” said Clara, her voice deep with a new knowing. “It means one day, we won’t have to.”
“Heresy,” Harold said. “You’re risking death.”
“So are we all,” she answered.
“They’ll burn you at the stake.”
“If I’m right, they won’t.”
“A trial then, regardless,” Harold said, his gaze dropping to the vial as the tavern’s jovial banter became a distant echo for them both.
“So be it,” Clara said, meeting his gaze. She leaned in, her fingers resting on his scarred knuckles. “Our farms take our children. It’s not right.”
“It’s how things are.”
“It’s how things were.”
“A trial will not be lenient, Clara. I can’t let you bring this to the king.”
“Not the king. The people.” She continued. “But don’t trust me. See for yourself.” Her eyes locked onto his. “Drink,” she said, her words echoing Elric’s.
Harold hesitated but finally drank. His eyes widened. He gripped the edge of the wooden table, his knuckles turning white. A sort of vacant gaze overcame him as if he’d journeyed to someplace far.
When the Elysium vision receded, he opened his eyes and looked at her anew, seeing the world for the first time again. He glanced around the hall as though it were a foreign land, his eyes lingering on the mundane — a crack in the table, the smudged goblet, a flickering torch on the wall—with awe and wonder. She knew then that they stood as one. Two visionaries, shouldering the burden of transforming the world, ready to shepherd their people into a revolutionary dawn.
In the square, the stone eyes of old heroes watched. A crowd formed, silenced by expectation and unaccustomed to the art of public speaking. Autumn leaves swirled at their feet.
“A new dawn!” Harold broke the silence. “Generations sacrificed, giving years for meager sustenance. But the land wants not our years — only our care and periodic reverence. The tales of a time without the toll of hunger, without a tax on life itself, from before the Great Famine, are not myths. They are forgotten chapters of our history, now on the verge of being rewritten.”
He raised the vial. Sunlight mirrored in its gold. “This is Elysium.”
Part IX: A Revolution Takes Shape
In the fading light of day, Harold and Clara stood by a murmuring brook, leaves rustling at their feet in quiet revolt. Faces young and old assembled around them; each one a silent rebellion against the servitude that taxed their years.
They drank, the chalice passing from hand to hand, a new ritual born. With each gathering, the numbers swelled; with each sip, more souls entwined. Slowly, yet with unyielding certainty, the kingdom shifted over the years. It changed not through a coup or uprising but through a still, relentless force, like water eroding stone. As the seasons passed and more villagers imbibed the Elysian brew, the weight of their invisible chains lessened, their atoms scattering into the evening air.
Shielded now, villagers sowed their own gardens, sanctuaries from the alchemist’s dominion. Bountiful harvests followed, hope supplanted despair. Word of the blooming private gardens spread like wildflowers, and fields once cursed by dark alchemy lay fallow and forgotten.
And there, by the unassuming brook, a revolution took shape. The soft sounds of the stream became an earthbound anchor for the myriad souls who opened the door to walk in the cosmic gardens of their minds. Each ritual added another stitch in the fabric of a new dawn; each sip, another brushstroke on the canvas of a world remade.
Part X: The Old Man
A decade drifted by. With each soul that tasted Elysium, the fetters of the old world loosened. The alchemist’s spell, once a yoke around their necks, now waned like thick morning fog giving way to the warmth of the day. Fields once cursed now bore food, not dread. Families gathered around bountiful tables, words flowing freely, unveiled.
Each year, townsfolk met by the sword in the square. Harold’s blade, the first monument raised in ages, stood as freedom’s spine, the axis of their new world. An old man approached, his eyes dimmed by memories of famine, leading a boy by the hand. Their eyes met, a chasm bridged: one soul untarnished by hunger, the other haunted by its ghost.
The old man stepped forward, his fingers quivering on the hilt of the sword. “Clara, what becomes of us if the land fails us again?” Years of hardship wavered in his voice, the ghosts of famine flickering in his eyes.
“It could,” Clara said, her voice steady as bedrock. “But it’s different now. Our fields are wider, our hands more skilled. We’re not trying to trick the earth with alchemy anymore. We speak in the simple terms it understands: soil, sun, water, time.”
Above, the alchemist’s fortress loomed, its towers now marred with cracks. Clara looked up. Empty windows stared back, like dead eyes on a fallen beast. Old times had ended; new ones had begun.
Part XI: The Note
Dawn broke, casting new light over worn cobblestones. Clara moved through the marketplace as if through a dream. The scent of cinnamon and rich coffee filled the air as she ran her fingers down silken tassels and through powdery barrels of golden saffron. Voices haggled; her feet felt the earth’s warm embrace.
Traders argued leisurely, their time no longer taxed by the spell. Children laughed, unburdened by field and plow.
Fields that once caged both young and old now released thinkers, builders, creators. The horizon changed form — bridges leapt over waterways, roads bound the land. Each stone laid was more than a fixture; it was a vow, a pact between the present and the future. It was today’s promise to a future yet unborn, anchored by the prosperity that now bloomed under Elysium’s sky.
As evening descended, the grand hall filled with voices unburdened by yesterday’s sorrow. In a secluded corner, Clara and Harold exchanged words about the loftier truths Elysium had laid bare.
A courier emerged from the crowd, extending a sealed parchment. “For you, mademoiselle.”
With a nod, Clara exchanged a coin for the note. Her eyes brightened as she absorbed the message:
Only a true renaissance resounds to the Whispering Pines. Continue, in health and strength. - Elric
She passed it to Harold, their eyes locking in wordless affirmation. “The Whispering Pines acknowledge us,” he finally said. “And so, we continue,” Clara replied, her voice unwavering, guided by truth. In the hall’s enveloping warmth, laughter, toasts, and spirited debates blended into a harmonious score — a sound that would have been foreign to their ancestors, a sound that marked the close of an era and the dawn of something profoundly new.
This story first appeared in Tales from the Timechain. Support our work and buy a copyhere.
79% of the zaps from this story will be passed onto the author, Reed.
21 Futures requests 21% for operating costs.
Ioni Appelberg (pronounced Yo-Ni Apple-Burg) is a bitcoin philosopher, futurist, author, and content creator. His content centers around science fiction, human history and it often takes the form of swashbuckling journeys to the frontiers of technology, space, and the human mind. His love of sci-fi, psychedelics, and futurism may take his stories (and unsuspecting readers) to strange but exciting places. He is also an avid reader, a medical doctor, a freedom fighter, an MMA fighter, a psychonaut, and a terrible chess player.
-
 @ 42a071ab:3391e086
2025-06-05 09:31:56
@ 42a071ab:3391e086
2025-06-05 09:31:56Trong một thế giới mà sự cạnh tranh ngày càng khốc liệt, yếu tố tạo nên sự khác biệt không chỉ nằm ở chất lượng sản phẩm mà còn ở cách một thương hiệu chăm sóc và kết nối với khách hàng. AV88 hiểu rõ điều đó và đã không ngừng đầu tư vào trải nghiệm người dùng như một chiến lược cốt lõi để xây dựng lòng tin và sự trung thành. Ngay từ những bước đầu tiên khi khách hàng tiếp cận AV88, họ được đón nhận bởi một giao diện thân thiện, dễ sử dụng và được thiết kế dựa trên hành vi sử dụng thực tế. Tất cả các chức năng, từ đăng ký tài khoản, quản lý thông tin cá nhân cho đến các bước tương tác hằng ngày đều được tối ưu để đảm bảo sự liền mạch và thuận tiện. Hơn thế, AV88 còn xây dựng một hệ thống chăm sóc khách hàng luôn sẵn sàng hỗ trợ 24/7, cung cấp thông tin kịp thời và giải quyết mọi thắc mắc nhanh chóng, mang lại cảm giác yên tâm tuyệt đối cho người sử dụng. Không chỉ dừng lại ở mức độ phản hồi, đội ngũ tại AV88 còn chủ động thu thập ý kiến, khảo sát nhu cầu và cải tiến dịch vụ theo thời gian thực, từ đó đảm bảo rằng mỗi sự đổi mới đều xuất phát từ chính kỳ vọng của người dùng. Nhờ vậy, AV88 không đơn thuần là một nền tảng dịch vụ mà còn là một người bạn đồng hành đáng tin cậy trong hành trình số hóa của mỗi khách hàng.
av88 cũng đặt ra một tiêu chuẩn mới cho sự minh bạch và bảo mật – hai yếu tố then chốt trong việc xây dựng niềm tin lâu dài. Mọi quy trình đều được thiết lập rõ ràng, dễ theo dõi và có hướng dẫn chi tiết, từ quy trình giao dịch cho đến các chính sách bảo vệ thông tin cá nhân. Các công nghệ mã hóa tiên tiến và lớp xác thực đa tầng giúp bảo đảm an toàn tuyệt đối trong mọi hoạt động. Không dừng lại ở việc duy trì chất lượng dịch vụ, AV88 còn tiên phong trong việc tích hợp công nghệ nhằm tối ưu hóa hiệu suất và giảm thiểu thời gian chờ đợi của người dùng. Các thao tác nạp – rút nhanh chóng, hệ thống thông báo thông minh và tính cá nhân hóa trong trải nghiệm giúp người dùng cảm nhận được sự linh hoạt và chuyên nghiệp. Chính sự kết hợp giữa công nghệ, con người và tầm nhìn chiến lược đã giúp AV88 không chỉ duy trì vị thế trên thị trường mà còn định hình chuẩn mực mới cho ngành dịch vụ lấy khách hàng làm trung tâm. Dù trong bối cảnh nào, AV88 vẫn luôn giữ vững cam kết: lắng nghe, thấu hiểu và đồng hành cùng khách hàng trên mọi hành trình. Điều này không chỉ tạo dựng giá trị bền vững cho thương hiệu mà còn góp phần nâng cao tiêu chuẩn chung của ngành, thúc đẩy sự phát triển toàn diện và dài lâu.
-
 @ 6ad3e2a3:c90b7740
2025-05-20 13:49:50
@ 6ad3e2a3:c90b7740
2025-05-20 13:49:50I’ve written about MSTR twice already, https://www.chrisliss.com/p/mstr and https://www.chrisliss.com/p/mstr-part-2, but I want to focus on legendary short seller James Chanos’ current trade wherein he buys bitcoin (via ETF) and shorts MSTR, in essence to “be like Mike” Saylor who sells MSTR shares at the market and uses them to add bitcoin to the company’s balance sheet. After all, if it’s good enough for Saylor, why shouldn’t everyone be doing it — shorting a company whose stock price is more than 2x its bitcoin holdings and using the proceeds to buy the bitcoin itself?
Saylor himself has said selling shares at 2x NAV (net asset value) to buy bitcoin is like selling dollars for two dollars each, and Chanos has apparently decided to get in while the getting (market cap more than 2x net asset value) is good. If the price of bitcoin moons, sending MSTR’s shares up, you are more than hedged in that event, too. At least that’s the theory.
The problem with this bet against MSTR’s mNAV, i.e., you are betting MSTR’s market cap will converge 1:1 toward its NAV in the short and medium term is this trade does not exist in a vacuum. Saylor has described how his ATM’s (at the market) sales of shares are accretive in BTC per share because of this very premium they carry. Yes, we’ll dilute your shares of the company, but because we’re getting you 2x the bitcoin per share, you are getting an ever smaller slice of an ever bigger overall pie, and the pie is growing 2x faster than your slice is reducing. (I https://www.chrisliss.com/p/mstr how this works in my first post.)
But for this accretion to continue, there must be a constant supply of “greater fools” to pony up for the infinitely printable shares which contain only half their value in underlying bitcoin. Yes, those shares will continue to accrete more BTC per share, but only if there are more fools willing to make this trade in the future. So will there be a constant supply of such “fools” to keep fueling MSTR’s mNAV multiple indefinitely?
Yes, there will be in my opinion because you have to look at the trade from the prospective fools’ perspective. Those “fools” are not trading bitcoin for MSTR, they are trading their dollars, selling other equities to raise them maybe, but in the end it’s a dollars for shares trade. They are not selling bitcoin for them.
You might object that those same dollars could buy bitcoin instead, so they are surely trading the opportunity cost of buying bitcoin for them, but if only 5-10 percent of the market (or less) is buying bitcoin itself, the bucket in which which those “fools” reside is the entire non-bitcoin-buying equity market. (And this is not considering the even larger debt market which Saylor has yet to tap in earnest.)
So for those 90-95 percent who do not and are not presently planning to own bitcoin itself, is buying MSTR a fool’s errand, so to speak? Not remotely. If MSTR shares are infinitely printable ATM, they are still less so than the dollar and other fiat currencies. And MSTR shares are backed 2:1 by bitcoin itself, while the fiat currencies are backed by absolutely nothing. So if you hold dollars or euros, trading them for MSTR shares is an errand more sage than foolish.
That’s why this trade (buying BTC and shorting MSTR) is so dangerous. Not only are there many people who won’t buy BTC buying MSTR, there are many funds and other investment entities who are only able to buy MSTR.
Do you want to get BTC at 1:1 with the 5-10 percent or MSTR backed 2:1 with the 90-95 percent. This is a bit like medical tests that have a 95 percent accuracy rate for an asymptomatic disease that only one percent of the population has. If someone tests positive, it’s more likely to be a false one than an indication he has the disease*. The accuracy rate, even at 19:1, is subservient to the size of the respective populations.
At some point this will no longer be the case, but so long as the understanding of bitcoin is not widespread, so long as the dollar is still the unit of account, the “greater fools” buying MSTR are still miles ahead of the greatest fools buying neither, and the stock price and mNAV should only increase.
. . .
One other thought: it’s more work to play defense than offense because the person on offense knows where he’s going, and the defender can only react to him once he moves. Similarly, Saylor by virtue of being the issuer of the shares knows when more will come online while Chanos and other short sellers are borrowing them to sell in reaction to Saylor’s strategy. At any given moment, Saylor can pause anytime, choosing to issue convertible debt or preferred shares with which to buy more bitcoin, and the shorts will not be given advance notice.
If the price runs, and there is no ATM that week because Saylor has stopped on a dime, so to speak, the shorts will be left having to scramble to change directions and buy the shares back to cover. Their momentum might be in the wrong direction, though, and like Allen Iverson breaking ankles with a crossover, Saylor might trigger a massive short squeeze, rocketing the share price ever higher. That’s why he actually welcomes Chanos et al trying this copycat strategy — it becomes the fuel for outsized gains.
For that reason, news that Chanos is shorting MSTR has not shaken my conviction, though there are other more pertinent https://www.chrisliss.com/p/mstr-part-2 with MSTR, of which one should be aware. And as always, do your own due diligence before investing in anything.
* To understand this, consider a population of 100,000, with one percent having a disease. That means 1,000 have it, 99,000 do not. If the test is 95 percent accurate, and everyone is tested, 950 of the 1,000 will test positive (true positives), 50 who have it will test negative (false negatives.) Of the positives, 95 percent of 99,000 (94,050) will test negative (true negatives) and five percent (4,950) will test positive (false positives). That means 4,950 out of 5,900 positives (84%) will be false.
-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 6be5cc06:5259daf0
2025-06-04 00:58:46
@ 6be5cc06:5259daf0
2025-06-04 00:58:46Introdução
O princípio do sola scriptura, pedra angular da teologia protestante desde a Reforma do século XVI, estabelece que apenas a Escritura constitui a autoridade final e suprema em questões de fé e prática cristã. Este princípio, formulado inicialmente por Martinho Lutero e sistematizado pelos reformadores subsequentes, pretende oferecer um fundamento epistemológico sólido para a teologia, livre das supostas corrupções da tradição eclesiástica.
Contudo, uma análise rigorosa revela que o sola scriptura incorre em contradições lógicas fundamentais que comprometem sua viabilidade como sistema epistemológico coerente. Este artigo examina essas contradições através de três perspectivas complementares: filosófica, exegética e histórica.
A Contradição Performativa Fundamental
O Problema da Autoreferência
O sola scriptura enfrenta um dilema epistemológico insuperável: afirma que apenas a Escritura possui autoridade final em matéria de fé, mas essa própria regra não é explicitamente ensinada na Escritura. Trata-se de uma contradição performativa clássica, onde o enunciado viola suas próprias condições de possibilidade.
Esta situação configura uma falácia de petitio principii (círculo vicioso), pois exige que se aceite uma doutrina que não pode ser sustentada pelas premissas do próprio sistema. Para estabelecer o sola scriptura, seria necessário recorrer a uma autoridade externa à Escritura – precisamente aquilo que o princípio pretende rejeitar.
Fundacionalismo Mal Estruturado
Do ponto de vista epistemológico, o sola scriptura apresenta-se como um fundacionalismo defeituoso. Pretende funcionar como axioma supremo e auto-evidente, mas falha ao não fornecer a base textual que sua própria metodologia exige. Um verdadeiro fundacionalismo escriturístico deveria ser capaz de demonstrar sua validade através de uma prova explícita nas próprias Escrituras.
O Testemunho Contrário das Escrituras
Limitações do Registro Escrito
A própria Escritura reconhece as limitações do registro textual. João 21:25 declara explicitamente: "Jesus fez também muitas outras coisas. Se cada uma delas fosse escrita, penso que nem mesmo no mundo inteiro haveria espaço suficiente para os livros que seriam escritos."
Este versículo é particularmente problemático para o sola scriptura, pois reconhece que nem todos os ensinamentos de Cristo foram preservados por escrito. Como pode a Escritura ser suficiente se ela própria admite sua incompletude?
A Valorização da Tradição Oral
Paulo, em 2 Tessalonicenses 2:15, oferece uma instrução que contradiz frontalmente o sola scriptura: "Assim, pois, irmãos, ficai firmes e conservai os ensinamentos que de nós aprendestes, seja por palavras, seja por carta nossa."
O apóstolo valoriza inequivocamente tanto a tradição oral ("por palavras") quanto a escrita ("por carta"), estabelecendo um modelo de autoridade dual que o protestantismo posterior rejeitaria.
A Necessidade de Autoridade Interpretativa
A narrativa do eunuco etíope em Atos 8:30-31 demonstra a inadequação da Escritura isolada como autoridade final. Quando Filipe pergunta se o eunuco entende o que lê, a resposta é reveladora: "Como poderei entender, se alguém não me ensinar?"
Este episódio ilustra que a mera posse do texto bíblico não garante compreensão adequada. É necessária uma autoridade interpretativa externa – no caso, representada por Filipe, que age com autoridade apostólica.
A Complexidade Hermenêutica
Pedro, em sua segunda epístola (3:16-17), reconhece a dificuldade interpretativa inerente às Escrituras: "Suas cartas contêm algumas coisas difíceis de entender, as quais os ignorantes e instáveis torcem, como também o fazem com as demais Escrituras, para a própria destruição deles."
Esta passagem não apenas reconhece a complexidade hermenêutica dos textos sagrados, mas também alerta sobre os perigos da interpretação inadequada. Implicitamente, sugere a necessidade de uma autoridade interpretativa confiável para evitar distorções doutrinárias.
O Paradoxo Histórico da Canonização
A Dependência da Tradição Eclesiástica
Um dos argumentos mais devastadores contra o sola scriptura emerge da própria história da formação do cânon bíblico. Os concílios de Hipona (393 d.C.) e Cartago (397 d.C.) foram responsáveis pela definição oficial do cânon das Escrituras tal como conhecemos hoje.
Este fato histórico cria um paradoxo insuperável: aceitar a Bíblia como autoridade única requer aceitar a autoridade da tradição eclesiástica que a definiu. O próprio cânon bíblico é produto da tradição apostólica e da deliberação conciliar, não de autodefinição escriturística.
A Circularidade da Autopistia
Tentativas protestantes de resolver este dilema através do conceito de "autopistia" – a suposta capacidade das Escrituras de se auto-autenticar – apenas aprofundam o problema circular. Como determinar que as Escrituras possuem esta propriedade sem recorrer a critérios externos? A própria doutrina da autopistia não é explicitamente ensinada na Escritura.
Implicações Teológicas e Epistemológicas
A Fragmentação Interpretativa
A história do protestantismo oferece evidência empírica das consequências práticas do sola scriptura. A multiplicação de denominações e interpretações divergentes sugere que o princípio, longe de fornecer clareza doutrinária, pode na verdade contribuir para a fragmentação teológica.
Se a Escritura fosse verdadeiramente suficiente e auto-interpretativa, seria razoável esperar maior convergência hermenêutica entre aqueles que aderem ao sola scriptura. A realidade histórica sugere o contrário.
A Alternativa Católica e Ortodoxa
As tradições católica e ortodoxa, embora enfrentando suas próprias tensões epistemológicas, mantêm pelo menos coerência interna ao reconhecer explicitamente múltiplas fontes complementares de autoridade: Escritura, Tradição e Magistério (no caso católico) ou Escritura e Tradição (no caso ortodoxo).
Estas posições evitam a contradição performativa do sola scriptura ao não reivindicar que sua própria metodologia epistemológica seja derivada exclusivamente da Escritura.
Conclusão
A análise crítica do sola scriptura revela contradições estruturais que comprometem fundamentalmente sua viabilidade como princípio epistemológico. O princípio incorre em contradição performativa ao estabelecer uma regra que não pode ser derivada de suas próprias premissas, configura um fundacionalismo mal estruturado ao carecer de base textual explícita, e enfrenta o testemunho contrário da própria Escritura, que reconhece suas limitações e a necessidade de autoridades interpretativas externas.
O paradoxo histórico da canonização – onde o próprio cânon bíblico depende da autoridade tradicional que o sola scriptura pretende rejeitar – representa talvez o golpe mais decisivo contra o princípio protestante.
Isso não implica necessariamente a falsidade do protestantismo como sistema teológico, mas sugere que seus fundamentos epistemológicos requerem reformulação substancial. Uma teologia protestante intelectualmente honesta precisaria reconhecer as limitações do sola scriptura e desenvolver uma epistemologia mais nuançada que leve em conta a complexidade das fontes de autoridade religiosa.
A busca pela verdade teológica, independentemente de compromissos confessionais, exige o reconhecimento rigoroso das limitações e contradições inerentes aos nossos sistemas epistemológicos. No caso do sola scriptura, essa honestidade intelectual revela um princípio que, por mais central que seja para a identidade protestante, não pode sustentar o peso epistemológico que tradicionalmente lhe foi atribuído.
-
 @ de7306de:1ea53f87
2025-06-05 08:46:54
@ de7306de:1ea53f87
2025-06-05 08:46:54Être « de gauche » ?
Essai pour une (re)définition transversale des concepts « gauche » et « droite »
Introduction
Il y a toujours deux niveaux. Le premier est celui sur lequel on s’appuie quand on se dit « de gauche » : c’est le niveau du discours, des bonnes intentions, des objectifs ou des revendications bien rationnelles, des belles valeurs, des symboles, des vérités chéries, etc. Puis il y a l’autre niveau, moins conscient, voire inconscient, qui fait que l’on va finir par réagir d’une certaine manière, parfois, souvent, en contradiction avec le premier niveau. Ce n’est pas, par exemple, parce qu’on n’aime pas la jalousie ou le pouvoir qu’on ne va pas se sentir jalouses ou qu’on ne va pas, parfois, prendre du plaisir dans certaines dynamiques de pouvoir. Combien de fois nous sommes-nous retrouvées frustrées de voir à quel point la réalité de nos actions se déroule en totale contradiction avec nos intentions ? Et ce, dans tous les domaines de la vie : intime, amoureuse, amicale, professionnelle, militante, etc. C’est-à-dire que nous pouvons être très « de gauche » au niveau des intentions, mais réactionnaires, voire fascistes, au niveau des pratiques. C’est donc ce deuxième niveau, dominé non pas par la raison, les concepts, les manifestes ou les bonnes intentions, mais par le monde inconscient, ses flux et ses mécanismes, auquel nous allons nous intéresser, car c’est bien là que la question se joue. Nous proposons donc un ensemble de prismes (Δ), sans aucune prétention totalisante, pour contribuer à une (ré)définition collective des concepts de gauche et de droite.
1er prisme Δ
Sensibilités et compétences
S e n s i b i l i t é :
propriété / aptitude d’une matière, d’un organe, d’un corps à réagir aux stimuli externes ou internes.
Le mot sensibilité vient de sens. Les sens captent. On peut réagir seulement aux stimuli/informations que l’on capte – inutile de forcer un aveugle à voir, un sourd à entendre. Les yeux captent la lumière, les tympans captent des ondes/vibrations. Or, il ne suffit pas d’avoir de bons yeux et de bonnes oreilles pour capter, par exemple, l’injustice dans notre entourage. Il nous faut quelque chose de plus. Quelque chose d’autre que nos sens physiologiques est à l’œuvre dans nos esprits lorsqu’on capte une injustice. Comme s’il y avait un autre type de sens. Si les sens physiologiques captent les informations physiques (lumière, vibration, température, distance, etc.), cet autre type de sens capte les informations sociales (quelle est ma place dans la meute, quand est-ce mon tour de manger, quel territoire m’est attribué ? etc.). Si, pour les sens physiologiques, des récepteurs chimiques et des terminaisons nerveuses sont à l’œuvre, pour cet autre type de sens, il s’agit plutôt de programmes, de « logiciels », un peu comme les applications de nos téléphones portables ou de nos ordinateurs. Il y a donc des « logiciels » qui nous permettent de capter les injustices, les violences, les oppressions, les signes de souffrance, de maladie, de dépression, de névrose ou de psychose, etc. Inutile de forcer un aveugle à voir, inutile de forcer quelqu’un qui n’aurait pas les bons logiciels à capter une injustice, une violence, une oppression. Il ne s’agit donc pas de vouloir ou de décider de capter ces situations ou ces phénomènes sociaux, il s’agit d’avoir, de cultiver les « bons logiciels ». Voilà donc ce à quoi nous nous référons quand on parle de sensibilités. Être de gauche donc, selon ce prisme, n’est pas tellement une décision, un vouloir ou une sorte d’identité autoproclamée que l’on pourrait rajouter facilement dans nos CV, afficher sur nos réseaux sociaux ou sur nos applis de rencontre, montrer avec nos t-shirts du Che Guevara, avec nos chants anarchistes ou nos quelques actions, non, non, non. Être de gauche = être sensible. Multi-sensible, pluri-sensible. Mais sensible à quoi ? À une diversité de phénomènes concernant le mental, le social et l’environnemental – et spécialement à leur intrication. Être de gauche implique donc avoir cultivé dans nos esprits une multiplicité de sensibilités : des sensibilités psychologiques, sociologiques, anthropologiques, écologiques… De ce point de vue, être de gauche n’est pas un discours, une mode, une décision, une envie, c’est du travail ! Car cette multiplicité de sensibilités, nous ne la cultivons pas par défaut socialement, culturellement – la société industrielle, capitaliste qui nous a façonnés, n’a surtout pas besoin d’esprits pluri-sensibles. Nous sommes obligés donc, si nous voulons cultiver ces sensibilités, de nager à contre-courant, de lutter contre le cadrage et la parcellisation propres à nos sociétés modernes, consistant à produire de petits soldats, de petits robots, de petites machines spécialisées, chacune dans son champ spécifique, et ce pour servir à qui ? Surtout pas à nous-mêmes, que ce soit individuellement ou collectivement. Nous voyons bien que ce n’est pas une mince affaire d’« être de gauche ». Quelque part, personne n’est de gauche, puisque personne n’est en mesure, prenant en compte la façon dont notre culture produit des sujets, d’avoir tout cet éventail de sensibilités. Pour mieux nuancer la question, nous sommes obligés de laisser de côté les lunettes de l’être, car elles nous contraignent à aborder le sujet de façon binaire : être ou ne pas être, soit tu es de gauche, soit tu ne l’es pas. On voit très bien que nous pouvons être sensibles par rapport à un sujet, à une situation ou à un domaine spécifique et, en même temps, très insensibles par rapport à d’autres sujets, situations ou domaines. Oui, cela veut dire que nous sommes de gauche et aussi, en même temps, de droite (insensibles) selon les endroits que l’on observe en nous, dans diverses situations et contextes. Il ne suffit pas d’« être marxistes » ou d’« être anarchistes » pour ne pas devenir des grands ou des petits tyrans, des grands ou des petits colons, des sexistes, des racistes, des oppresseurs des minorités, des validistes, des violents, des agresseurs, que ce soit au niveau collectif ou sur un niveau plus personnel, plus intime. De droite et de gauche, en même temps ? Quelle idée ! C’est que « être de gauche » est une expression trop rigide. Il convient donc d’analyser la question en termes de devenir : si l’être est un état donné, une pierre, le devenir représente toujours le mouvement, le fleuve et ses tourbillons. Nous serions très prétentieux, très arrogants ou très naïfs, si nous disions que nous sommes de gauche. En revanche, nous pouvons dire sans aucune prétention que nous sommes dans un devenir de gauche, dans la mesure où l’on cultive les sensibilités diverses. Nous avons dit qu’être de gauche veut dire être multi-sensible ; que nous ne pouvons pas vraiment être de gauche, car malgré le fait que l’on soit sensibles à certains sujets ou situations, nous sommes forcément insensibles par rapport à d’autres sujets et à d’autres situations, car victimes de l’industrie et de son culte des œillères ; que nous sommes en même temps de gauche et de droite, selon les endroits que l’on observe en nous dans une situation donnée, dans un contexte donné ; que le prisme du devenir est plus adapté que les lunettes de l’être, et qu’au lieu de dire « je suis de gauche », il est plus précis de dire « je suis dans un devenir ‘de gauche’ ».
Compétences ?
Nous avons, jusqu’à maintenant, abordé la question de la gauche en ce qui concerne les sensibilités, c’est-à-dire la captation des signes ou des informations concernant le mental, le social et l’environnemental. Mais suffit-il d’être sensible, même multi-sensible ? Combien de fois avons-nous capté des injustices, des conflits et toutes sortes de problèmes par rapport auxquels nous n’avons rien pu faire ? Nous pouvons être très sensibles et en même temps nous sentir très impuissants. Il y a donc deux choses qui seraient précieuses pour la gauche selon ce prisme : la captation et l’action, les sensibilités et les pratiques. Pour faire ou pratiquer, il faut pouvoir faire, être capable, compétent. Faire un bon discours, gérer un conflit, établir des relations de façon saine, produire autrement, consommer autrement, gérer la propriété autrement, apprendre à prendre soin et à nous soigner, apprendre à soutenir des personnes, déconstruire nos vieux logiciels, expérimenter et trouver les modes d’organisation les plus adaptés, articuler les différents terrains d’action politique (macro, micro et infra-personnel), devenir souples et ouverts au monde, à l’altérité, etc. Tout cela requiert à la fois des sensibilités et des compétences très concrètes, précisément celles que la société néglige, que notre culture ne cultive pas. Dans la gauche au sens traditionnel, y compris ladite « extrême gauche » ou « gauche radicale », prenons-nous au sérieux cette question ? Sommes-nous en train de cultiver cette multiplicité de sensibilités et de compétences ?
Et la droite, c’est quoi ?
Nous avions jusqu’à maintenant utilisé ce prisme pour définir la gauche comme sensible, comme multi-sensible. Comment faire alors sens de la droite ? Est-ce l’insensibilité qui la définit ? Les personnes plus à droite sont-elles insensibles ? Nous avions défini la sensibilité comme une sorte de logiciel nous permettant de capter et de réagir à un stimulus, à une information, à une situation donnée. L’acte raciste, classiste, sexiste, n’est-il pas nécessairement la conséquence d’un type de sensibilité, selon notre définition ? Sensibilité par rapport à l’« invasion » de la part des étrangers, au « grand remplacement », aux « déviances » sexuelles ou de genre, à l’« hystérie » des femmes, à l’« insolence » des travailleurs, etc. Nous pourrions dire que la droite est aussi sensible, et même multi-sensible ! Ce constat fait-il effondrer notre propos ? Ou est-ce qu’il y aurait des « bonnes » et des « mauvaises » sensibilités ? Les sensibilités, expliquent-elles vraiment le clivage gauche-droite ? Nous considérons qu’au contraire, notre propos tient très bien. Pour nous, la droite s’explique en termes d’insensibilité et aussi en termes de sensibilité. D’abord d’insensibilité, car la droite est insensible à une diversité de phénomènes, à un ensemble d’injustices, de violences et d’oppressions, et en même temps, elle se définit par un ensemble de sensibilités que nous pourrions qualifier d’inadaptées. Il y aurait donc des sensibilités adaptées et des sensibilités inadaptées selon la situation, selon le contexte. Mais adaptées ou inadaptées selon quels critères, selon quelle science ou quelle philosophie ? Qualifier une sensibilité, un logiciel d’inadapté, n’est-il pas trancher de façon complètement arbitraire dans l’amoralité du cosmos ? Ce problème philosophique n’est pas facile à résoudre sans invoquer une justice divine, un évangile religieux ou un évangile militant. Or, il y a une chose, pour nous la seule, qui tranche la question malgré nous, en dépit de nous, au-delà de nous, en deçà de nous, autour de nous, à travers nous. C’est la vie elle-même, ou plus précisément l’écologie. Tout système « vivant », y compris les rapports sociaux, obéit à des « principes » écologiques : si on ne boit pas assez d’eau, on finit par mourir ; si nous refoulons des émotions, des pulsions vitales, nous serons condamnés à être névrosés, malades ; si nous colonisons un peuple et si, lorsque ce peuple se défend, nous le réprimons violemment, une partie de ce peuple cherchera à se défendre d’une façon plus violente, et si notre réponse à une telle « radicalisation » est de fusiller ou de bombarder les « radicaux », les « terroristes », alors au lieu de diminuer la « menace terroriste » qui nous fait peur, nous sommes en train de la nourrir, le paradoxe étant que c’est nous, avec le premier acte de colonisation, qui l’avons provoquée. Ces trois exemples représentent des réalités, des déterminations écologiques qui n’ont rien à voir avec nos croyances, nos valeurs, nos idéologies, nos symboles. Nous pouvons identifier de mieux en mieux quand un écosystème comme une forêt est perturbé, troublé, malade ou menacé de mort. C’est l’interrelation de fonctions en équilibre(s) qui fait forêt. Tout ce qui perturbe, trouble ou menace ces équilibres est considéré comme toxique, comme nocif, comme maladif. Cela semble évident pour la forêt, or nous devons souligner que l’esprit humain ainsi que les sociétés humaines obéissent aux mêmes types de déterminations écologiques. Ces déterminations sont elles-mêmes déterminées par la singularité de chaque écosystème : il y a des forêts qui ont moins besoin d’eau, de chaleur et de lumière que d’autres, c’est d’ailleurs ce qui différencie la forêt de la jungle. Et il y a aussi des déterminations qui s’appliquent dans toute forêt, dans toute jungle : si les bactéries qui captent l’azote de l’air (N≡N – non assimilable) et qui le fixent dans le sol sous forme d’ammoniac, nitrites et nitrates (·NH3, ·NO2, ·NO3 - assimilables) disparaissent, alors n’importe quelle forêt ou jungle serait condamnée à une mort subite/rapide, car ces bactéries représentent la source d’azote pour la quasi-totalité des êtres vivants, l’azote faisant partie essentielle de l’ADN, leur absence serait fatale – pas d’azote assimilable, pas de vie. Nous considérons que ce sont ces déterminations, générales et singulières, dans chaque registre écologique et dans leur intrication – mental, social et environnemental – qui détermineront les sensibilités adaptées ou inadaptées dans un moment, une situation, un contexte, un territoire donné. Nous pouvons dire alors que les sensibilités de la gauche, ce sont des sensibilités seulement par rapport aux / concernant les trois registres écologiques dans leur intrication, tandis que la droite est précisément insensible aux rapports écologiques, à l’écologie dans ce sens large, et sensible ou hyper-sensible par rapport à ce qui fait inconsciemment peur, à ce qui menace leurs territoires existentiels, et plus précisément leurs points d’accrochage (deuxième Δ), autour desquels ces territoires ont été constitués / formés.
Gauche = sensibilités et compétences qui œuvrent dans le sens écologique – Écosophique : articulation transversale de trois registres écologiques – mental, social et environnemental.
Droite = sensibilités et compétences qui œuvrent dans un sens non-écologique, anti-écologique, écocide.
-
 @ 7460b7fd:4fc4e74b
2025-06-05 15:54:42
@ 7460b7fd:4fc4e74b
2025-06-05 15:54:42比特币正在主动引诱量子计算“破解自己”
引言:危机还是契机?
比特币和量子计算,这两个看似对立的存在,正在酝酿一场耐人寻味的博弈。许多人担心未来强大的量子计算机将秒破比特币的密码学基石,从而令区块链安全灰飞烟灭。然而,本文想传达的核心观点却截然相反:比特币不仅不会被量子破解打败,反而正在通过协议层的巧妙设计来“引诱”量子计算进入自己的游戏规则之中。通过诸如BIP-360等提案,比特币有望将量子计算的威胁转化为动力,开启一个“后挖矿时代”的全新正反馈经济体系,让“破解”本身成为新的挖矿机制。
这样的观点听起来近乎狂想,但背后有着深厚的技术逻辑支撑。我们将从基本的密码学原理谈起,逐步剖析量子计算的能力与局限,以及比特币协议在抗量子方向做出的结构性准备。最后,我们探讨一种大胆的经济模型:当量子计算被诱导去参与“破解竞赛”时,或许正是比特币凤凰涅槃、新经济形态崛起之机。
非对称加密的数学本质:“上帝视角”的陷门答案
非对称加密(如RSA、椭圆曲线加密ECC等)的核心在于存在一种单向函数:正向计算容易,反向推导极难。公钥可以视作某个难题的题目,私钥则相当于“上帝视角”提前知道的答案。一旦掌握私钥,就能轻松完成从答案到题目的逆推;而只有公钥时,想要逆推出私钥则被设计为在现实中不可行。这类单向难题通常通过陷门函数来实现——对合法持有者(私钥)来说,存在隐藏的捷径(陷门)可以快速解题;而对局外人来说,题目看似无解。
举例来说,比特币当前采用的ECC加密:私钥与公钥的关系就像“一次难以逆推的乘法”。给定私钥x,乘以基点G可轻易得到公钥点P = x·G,但已知P却无法高效求出x。这种不对称确保了签名者可以用私钥生成签名,而验证者只能用公钥验证签名而无法伪造。私钥掌握了解题的“上帝答案”,公钥则只能用于验证答案是否正确。
这一点在新型的抗量子算法中同样体现。以格密码(lattice cryptography)为例:Falcon等基于NTRU格的签名算法,其公钥可以被视为一个高维长基,私钥是对应的短基。pqshield.com在二维格子上的示意说明了这种不对称性:拥有短基(私钥)时,我们可以高效地找到距离某个目标点很近的格点解;但只有长基(公钥)时,我们顶多能验证某个给定解是否有效,却很难自行找到足够优质的解pqshield.com。换言之,私钥提供了一个陷门,允许持有者快速逆推答案,而公钥持有者只能望“题”兴叹。
图:在二维格子中,签名者持有的短基(私钥)可以高效求解出距离目标点(黑色方块)极近的格点解(绿色圆点)。绿色平行四边形表示短基下求解空间很小,因而容易找到最优解。这直观展示了陷门函数的威力:私钥掌握短基就如同拿到了解题捷径。
图:仅持有长基(公钥)时,使用相同算法得到的格点解(红色圆点)可能距离目标(黑色方块)很远。红色平行四边形代表在无陷门情况下求解范围巨大,找到最佳解极其困难。但验证者仍可用长基检查出某个解(如绿色点)确实是有效解pqshield.com。这体现了公私钥在计算能力上的不对称:私钥可求解,公钥仅可验证。
总而言之,非对称加密的安全性源自数学难题的单向性质和陷门结构。私钥就是那个隐藏的逆向通道,“上帝视角”的答案;公钥则是不具备捷径的信息,只够验证而无法逆推。从RSA的整数分解、ECC的离散对数,到Falcon的近似最近矢量问题,每一种公钥体制都是在构造“题目易出答案难逆”的格局,让持有陷门者轻松,旁观破解者绝望。
量子计算的原理与极限:并行穷举的神话与现实
量子计算机令人畏惧之处,在于其并行计算能力。通过量子叠加态,n个量子比特(qubit)可同时表示2^n种状态——仿佛能把指数级的可能性同时考虑。配合量子干涉与算法设计,量子计算机能够以远胜传统计算机的效率解决某些特定问题。其中最著名的就是Shor算法,它能在多项式时间内完成对大整数的质因数分解和离散对数求解。这正是传统公钥加密(RSA、ECC)的命门:一旦有足够强大的量子计算机,基于这些数学问题的公钥体制将不再困难,私钥可以由公钥“解密”而出coindesk.com。
然而,“并行穷举”的神话背后有严格的物理和工程学限制。首先是量子比特数量和质量的限制:当前的量子芯片规模远未达到破解现代加密所需的级别。据风险研究机构与专家调查,目前我们只有几十到几百个物理qubit,而要威胁256位ECC或2048位RSA,需要数百万高质量qubitdeloitte.com。不仅数量上相差几个数量级,现有量子芯片的纠错和降噪技术也远不成熟。量子比特极其敏感,微小噪声都会引入错误,真正实用的量子计算机需要对成千上万的物理比特进行纠错编码,形成稳定的逻辑比特。这个工程挑战之巨大,使得可攻破密码的量子计算机仍是多年之后的前景——多数专家预测大概还需十几年时间才可能出现实质威胁deloitte.com。
其次,量子计算并非万能破解,仅对特定问题有指数级加速。Shor算法擅长因数分解和离散对数,Grover算法可以对无结构的穷举搜索加速(将时间复杂度平方根降低)。但许多新兴的抗量子算法依赖的问题(如格上的最短向量问题SVP、最近向量问题CVP,或多变量方程、哈希预像等)目前并无高效量子算法。这些问题大多属于NP难类,甚至找近似解也极为困难emerginginvestigators.org。尽管量子计算提供并行试探能力,但对这类高度复杂的问题也爱莫能助。正如一项研究指出:SVP和CVP问题即便在量子计算机上依然“极端困难”,在可预见的将来仍足以保证安全性emerginginvestigators.org。Falcon所使用的NTRU格就是这样的难题代表——没有已知算法可以像Shor之于RSA那样,高效攻破NTRU问题。
最后,我们还需注意量子攻击的实际条件。量子破解比特币主要有两种情景:存储攻击和传输攻击deloitte.com。存储攻击指利用量子计算找出已公开公钥对应的私钥,从而盗取静态存放于链上某地址的币;传输攻击则是当交易广播(公钥暴露)后,在被矿工打包上链前的短暂窗口内,量子计算抢先推导私钥并盗转。这两种攻击对量子能力要求不同:存储攻击允许耗时几周甚至数月破解一个密钥,只要在币移动前完成即可;而传输攻击要求在区块确认之前(比特币约10分钟内,以太坊更短)秒破私钥deloitte.com。显然,目前和可预见的中期内,量子计算都远达不到传输攻击所需的即时破解水平;即便存储攻击,由于比特币区块链的UTXO模型(稍后详述),真正高价值、长时间暴露公钥的币也相对有限deloitte.com。因此,量子威胁虽然现实存在,但并非一夜之间让比特币崩溃的魔法。这反倒给予我们部署抗量子方案、引导量子力量“为我所用”的时间窗口。
抗量子密码学的三大结构前提
要让比特币真正抵御量子威胁,并把量子计算纳入自身生态,需要满足几个结构性前提。经过多年社区讨论和研究,以下三点被认为是比特币走向抗量子的关键设计要素:
-
UTXO模型:隐藏公钥缩短攻击窗口 – 比特币采用UTXO模型,每次交易都会生成新地址,公钥通常以哈希形式隐藏在地址中,直到你花费时才公布。这意味着量子计算只有在你发起交易后的很短时间内(交易确认前)才能获得公钥并尝试破解,大大压缩了攻击窗口anduro.iodeloitte.com。相较之下,账户模型(如以太坊)重复使用固定地址,公钥一旦被提取或首次使用后就长久暴露,使得65%以上的以太币当前都处于量子暴露风险中,而比特币约只有25%处于类似风险deloitte.com。UTXO模型通过“一次性地址”和“不用则公钥不出”的原则,天然提供了对抗量子存储攻击的第一道屏障。
-
“见证隔离”(SegWit):模块化升级签名算法 – 抗量子方案的发展日新月异,比特币必须保持签名算法的可插拔升级能力。2017年的见证隔离升级正是为此奠定基础:SegWit将签名等见证数据与交易本体分离,并引入版本化的见证脚本格式。这使得添加新签名类型成为可能——通过软分叉引入新的输出类型和见证版本,就能兼容地支持不同算法delvingbitcoin.org。正如BIP-341利用SegWit扩展出了Taproot的Schnorr签名,比特币也可以扩展出抗量子签名的新地址类型而无需硬分叉或显著增加区块体积delvingbitcoin.org。这一模块化特性对于迎接未来各类抗量子算法至关重要,没有SegWit的铺垫,抗量子改造将困难重重。
-
分级安全机制:根据价值和时效选择算法强度 – 由于UTXO的性质,每笔交易在花费时都会暴露其公钥。因此,安全策略不能“一刀切”,应允许根据币值大小或持有时长采用不同强度的抗量子算法。高价值的UTXO、长期未移动的“老币”,应使用更高安全级别但可能更重型的签名方案;反之,小额频繁交易可用较轻量的方案以兼顾效率和区块容量。好比Falcon提供了512和1024两种参数版本:Falcon-1024安全级别更高但签名稍大,而Falcon-512签名更小速度更快,适合资源受限场景emerginginvestigators.org。未来比特币或可同时支持多种抗量子算法或参数,用户按需选用,让“安全性”成为一种可以权衡和市场定价的链上资源。每一次支付都在安全与成本之间找到平衡,这将促使一个分层的安全市场形成——进一步论述见后文经济模型部分。
上述三大前提缺一不可:UTXO模型提供了基础的_安全缓冲_,SegWit机制给予_升级弹性_,分级算法让_经济可行性_落地。在这方面,比特币的体系结构远优于某些后来的公链。例如,以太坊的账户模型天生缺乏隐藏公钥的机制,地址就是固定的公钥哈希,一旦使用过私钥签名就永久暴露公钥,同时其交易脚本(EVM)对签名算法固定死,没有灵活插拔空间。这意味着以太坊想转向抗量子算法,必须经过极其痛苦的整体迁移或硬分叉——开发者需要为每个账户引入新密钥,新老算法并行过渡,智能合约地址、签名验证逻辑全部推倒重来。这种难度令人生畏,以至于有人嘲讽以太坊“几乎不可能”实现真正的抗量子迁移。反观比特币,得益于其简单而弹性的UTXO+Script设计,只需通过新的输出类型软分叉,就可以逐步引入抗量子地址,让用户自愿迁移过渡,避免一次性硬分叉的系统性风险。
BIP-360:可选抗量子签名,引入量子博弈
面对量子威胁,比特币开发社区并未坐以待毙。2024年,由开发者Hunter Beast提出的BIP-360提案(又称P2QRH,意为“支付到抗量子哈希”)正式将抗量子签名引入了议事日程anduro.io。BIP-360核心思路是在比特币中增加新的地址类型,这些地址采用后量子密码学的签名算法(当前优先考虑Falcon,并备选CRYSTALS-Dilithium和SPHINCS+等)来取代易受量子攻击的ECDSA/Schnorr签名anduro.iogroups.google.com。换句话说,用户可以自愿选择生成一种“抗量子地址”,对应的UTXO需使用抗量子算法签名才能解锁。
为什么说BIP-360让比特币“引诱”量子计算加入博弈?这里有几层含义:
首先,BIP-360采用软分叉方式部署,可选而非强制。这意味着在量子计算真正成熟之前,绝大多数交易仍可继续使用原有签名算法,不平添负担;而有安全偏好的用户或机构可以提前迁移一部分资金到抗量子地址以高枕无忧。随着量子技术进展,逐步会有更多人选择这个选项,形成一个与量子威胁赛跑的过程。这种自愿迁移机制本身就是一种对量子黑客的诱导:网络主动暴露出一个“堡垒更坚固”的区域,鼓励守法用户往那里走,同时意味着留下的旧区域反而成为显眼的攻击目标和“诱饵”。
其次,BIP-360在算法选择和参数上充分考虑了区块链经济的承受力。起初提案曾讨论过一些前沿算法如SQIsign,但发现其验证开销高达ECDSA的15,000倍,若全网采用将使验证一块新区块从1秒暴涨到4小时,带来难以接受的性能瓶颈groups.google.com。最终的方案优选Falcon等NIST标准算法,它们签名体积较小、验证高效,可与当前区块大小和验证速度相容groups.google.com。例如Falcon-1024的签名约1.3KB、公钥1.7KB左右,这虽然比当前64字节的Schnorr签名大得多,但并非无法承受。通过配置灵活的安全级别(如重要交易才用Falcon-1024,一般小额用Falcon-512或普通Schnorr),比特币区块空间将被合理分配在安全性和费用之间。BIP-360精心设计了新的地址格式和见证结构,确保即便引入抗量子签名,区块验证和存储开销也在经济范围内,不会动摇挖矿和节点运行的成本平衡anduro.io。
最后也是最具前瞻性的一点,BIP-360为量子计算参与链上博弈打开了一扇门。通过提供抗量子和非抗量子地址并存的环境,比特币网络其实设置了一个对量子计算的挑战擂台:量子计算可以选择去攻击那些仍使用旧签名算法且价值巨大的UTXO,但同一时间,网络里的用户也在不断提升关键UTXO的签名强度来应对。量子计算不再是一个纯粹的外部敌人,而被巧妙地“请”进了系统,在规则内与用户和矿工互动。这为下一节将讨论的新经济模型奠定了基础——破解即挖矿的雏形由此孕育。
值得一提的是,BIP-360还提出了一个Taproot的量子安全补丁方案P2TRH,用哈希隐藏Taproot的公钥以弥补其“公钥长曝”缺陷groups.google.comgroups.google.com。因为现有的Taproot地址(见证v1)是直接以公钥生成地址,失去了UTXO模型隐藏公钥的优势,量子攻击者可以随时尝试破解Taproot资金。P2TRH通过将Taproot公钥再哈希一层,恢复“见证前隐藏公钥”的特性,代价是每笔此类输入增加8.25字节开销groups.google.com。这显示出比特币开发者未雨绸缪,连新升级的Taproot漏洞也在想办法弥补,使全局达到抗量子的结构性统一。
综上,BIP-360及相关提案不仅提供了技术方案,更释放出一种积极的信号:比特币正主动拥抱量子挑战,将其纳入规则之内。正如Anduro团队支持BIP-360时所言:“量子攻击的威胁严肃而迫近,我们不能坐等紧急关头才手忙脚乱。”anduro.ioanduro.io比特币社区选择了在危机到来前主动布局,以最小的代价换取最大的安全冗余和发展新契机。
“破解竞赛”经济模型:当量子成为新矿工
设想未来5-15年内,量子计算技术逐步成熟。在比特币网络中,可能会上演这样一幕令人惊叹的图景:量子计算矿工和抗量子验证者同时在线,围绕着尚未升级的老式UTXO展开一场你追我赶的“破解竞赛”。这将引发怎样的经济动力?我们大胆描绘一个后PoW时代的可能场景:
一方面,强大的量子计算机不再浪费算力去挖掘哈希谜题(传统PoW),而是直接瞄准那些“量子易攻”的UTXO,即尚使用老式ECDSA/Schnorr签名且公钥已暴露的地址。这些地址里的币对合法持有人来说如果迟迟未迁移到抗量子地址,实际上就变成了躺在链上的“悬赏”:谁能先算出私钥,谁就能转走这些币。在量子计算参与者眼中,这些币和早期比特币矿工眼中的区块奖励无异,都是凭借算力可竞争获取的收益。值得注意的是,根据分析,目前约有25%的比特币(按币量)处于公钥已暴露状态deloitte.com。随着时间推移,这个比例可能上升——除非持有人主动升级安全。这就像网络故意留出了一片“牧场”,让量子计算在其中竞相捕猎,以获得收益。量子攻击者之间形成竞争:更快的量子芯片、更好的算法意味着可以更早破解特定私钥,拿下那笔币。这几乎就是PoW的变体——过去矿工拼SHA-256算力抢区块奖励,未来量子矿工拼质因数分解/离散对数能力抢遗留UTXO。
另一方面,守护这片“牧场”的则是抗量子验证者和普通用户自身的防范行为。所谓抗量子验证者,可能是运行完整后量子节点或提供安全服务的专业机构。他们一方面帮助用户升级UTXO(例如提供一键迁移服务,把旧地址币转移到新PQ地址上,收取服务费),另一方面监测全网可疑交易。当量子攻击者尝试盗取某UTXO时,如果该UTXO持有者事先购买了“安全服务”,验证者可以抢先代为花费将币转移到更安全的地址(类似白帽黑客行为),或者提供更高级别签名升级以挫败攻击。总之,抗量子能力本身也成为一种商品,在市场上明码标价。你想让自己的币绝对安全?可以付费请量子安全服务团队定期轮换密钥、使用最高强度签名、监控链上异常。你的交易想确保不中途被截胡?可以支付更高矿工费甚至指定量子保险节点护送。在链上,一个根据签名难度和安全级别定价的市场逐渐形成:越高难度的签名(比如超长位的Falcon变种、多重签名方案结合等)需要支付越高的费用来存储和验证;反过来,这些费用补贴给保障网络安全的矿工/节点,激励他们投入更多资源提升抗量子能力。这种正反馈循环下,“安全”本身成为了新的经济激励。
如此一来,比特币生态迎来了“后挖矿时代”的转型:当区块补贴逐渐趋零,原本空缺的矿工激励由量子破解竞赛和安全服务市场所填补。量子计算加入竞争并非摧毁网络,反而扮演起类似矿工的角色,通过攻破薄弱环节来获得收益;而诚实的参与者则通过不断升级安全措施和支付安全费用来保护资产。这看似矛盾,却形成了动态平衡:正如生物进化中的“红后效应”,猎豹越快,羚羊也进化得更快,两者共同提升了系统的活力。
当然,这一模型中也充满戏剧性和讽刺意味——尤其当我们把眼光投向其他缺乏这种机制的公链。以太坊等账户制链若在量子时代陷入危机,很可能只能选择停机硬分叉、或者由中心化机构出面更换用户密钥,几乎无自动博弈的空间可言。而比特币网络则通过精妙的协议调整,把外部威胁内化为内部博弈,让市场机制去调节和应对。这种弹性与活力,正是比特币经久不衰的原因。
结语:危机催生新生,量子力量为我所用
当年互联网面对计算机病毒肆虐时,人们最终没有被动防守,而是发展出杀毒产业、安全协议,将病毒的威胁转化为推动网络更加健壮的动力。同样道理,比特币面对量子计算的冲击,并非只能筑高墙固步自封,而是选择了更具前瞻性的道路:拥抱威胁、化敌为友。通过提前布局抗量子基础设施(UTXO模型、SegWit扩展、PQ签名算法)、逐步推行BIP-360等方案,比特币正悄然改变游戏规则。在这个新规则中,量量对决、攻守博弈将上演全新篇章,网络安全不再是一成不变的盾牌,而是一套动态进化的生态系统。
或许若干年后回望,我们会发现量子计算并没有摧毁比特币,反而成就了比特币历史上的一次重大飞跃——开启了一个后工作量证明时代的新纪元。在这个纪元里,“破解就是新挖矿”不再只是戏谑之语,而成为链上真实上演的经济现象;“出售安全”也从附属服务变成每个节点和用户的日常考量。比特币将继续履行其角色:作为一个去中心化的、自我强化的金融体系,它有能力将任何挑战转化为自身进化的燃料。
正如BIP-360提案作者所言,这是一个“when 而非 if”的议题anduro.io。量子计算终将到来,而比特币已在主动邀请它参与一场精心设计的游戏。当量子计算机真的站上擂台,比特币早已不再是那个任人宰割的靶子,而更像是一位早已摆好阵势的棋手,静候对手入局。在这盘大棋中,没有永远的猎物,只有不断进化的猎人。比特币,会是那个始终笑到最后的“猎人”吗?让我们拭目以待。
参考文献:
-
【18】PQShield博客:《Falcon – A Post-Quantum Signature Scheme》 – 阐释格密码中长基(公钥)与短基(私钥)的不对称性pqshield.com。
-
【28】Deloitte报告:《Quantum risk to the Ethereum blockchain》 – 比较了比特币UTXO模型与以太坊账户模型在量子攻击下的差异,指出以太坊65%资产易受量子威胁,而比特币约25%deloitte.comdeloitte.com。
-
【23】Bitcoin开发者论坛:《Proposing a P2QRH BIP towards a quantum resistant soft fork》 – 描述了通过SegWit扩展新签名算法的思路,无需硬分叉且不增加区块大小delvingbitcoin.org。
-
【22】Emerging Investigators论文:《A meta-analysis on NIST post-quantum cryptographic primitive finalists》 – 说明Falcon-512与Falcon-1024在安全性和性能上的差异,并强调SVP/CVP等问题对量子计算依然极为困难emerginginvestigators.orgemerginginvestigators.org。
-
【36】Anduro博客:《Bitcoin Needs Quantum Resistant Addresses – We Support BIP360》 – 介绍了BIP-360提案内容,引入抗量子地址类型P2QRH,采用Falcon和Dilithium签名,软分叉兼容anduro.io。同时强调量子威胁需提早应对的紧迫性anduro.ioanduro.io。
-
【32】Bitcoin开发邮件列表:《P2QRH/BIP-360 Update》 – 提供了BIP-360提案的最新动态,算法选型从SQIsign转向Falcon、Dilithium、SPHINCS+,原因是前者验证开销过大(15,000倍)而不切实际groups.google.comgroups.google.com。
-
【30】CoinDesk报道:《Quantum Computing Could Break Bitcoin-Like Encryption Far Easier…》 – 提及比特币所用ECC也可被Shor算法破解,只要有足够强大的量子计算机coindesk.com。
-
【33】Deloitte报告:《Quantum risk to the Ethereum blockchain》 – 阐述当前量子计算的物理局限:需要上百万qubit且降低噪声量级,目前技术远不能攻击密码算法deloitte.com。
-
【38】Bitcoin开发邮件列表:《P2QRH/BIP-360 Update》 – 描述了针对Taproot的P2TRH抗量子方案,用哈希隐藏公钥以减小长时间暴露,并分析其开销和局限groups.google.comgroups.google.com。
-
-
 @ 32e18276:5c68e245
2025-06-02 20:58:05
@ 32e18276:5c68e245
2025-06-02 20:58:05Damus OpenSats Grant Q1 2025 Progress Report
This period of the Damus OpenSats grant has been productive, and encompasses the work our beta release of Notedeck. Since we sent our last report on January, this encompasses all the work after then.
Damus Notedeck
We released the Beta version of Notedeck, which has many new features:
Dave
We've added a new AI-powered nostr assistant, similar to Grok on X. We call him Dave.
Dave is integrated with tooling that allows it to query the local relay for posts and profiles:
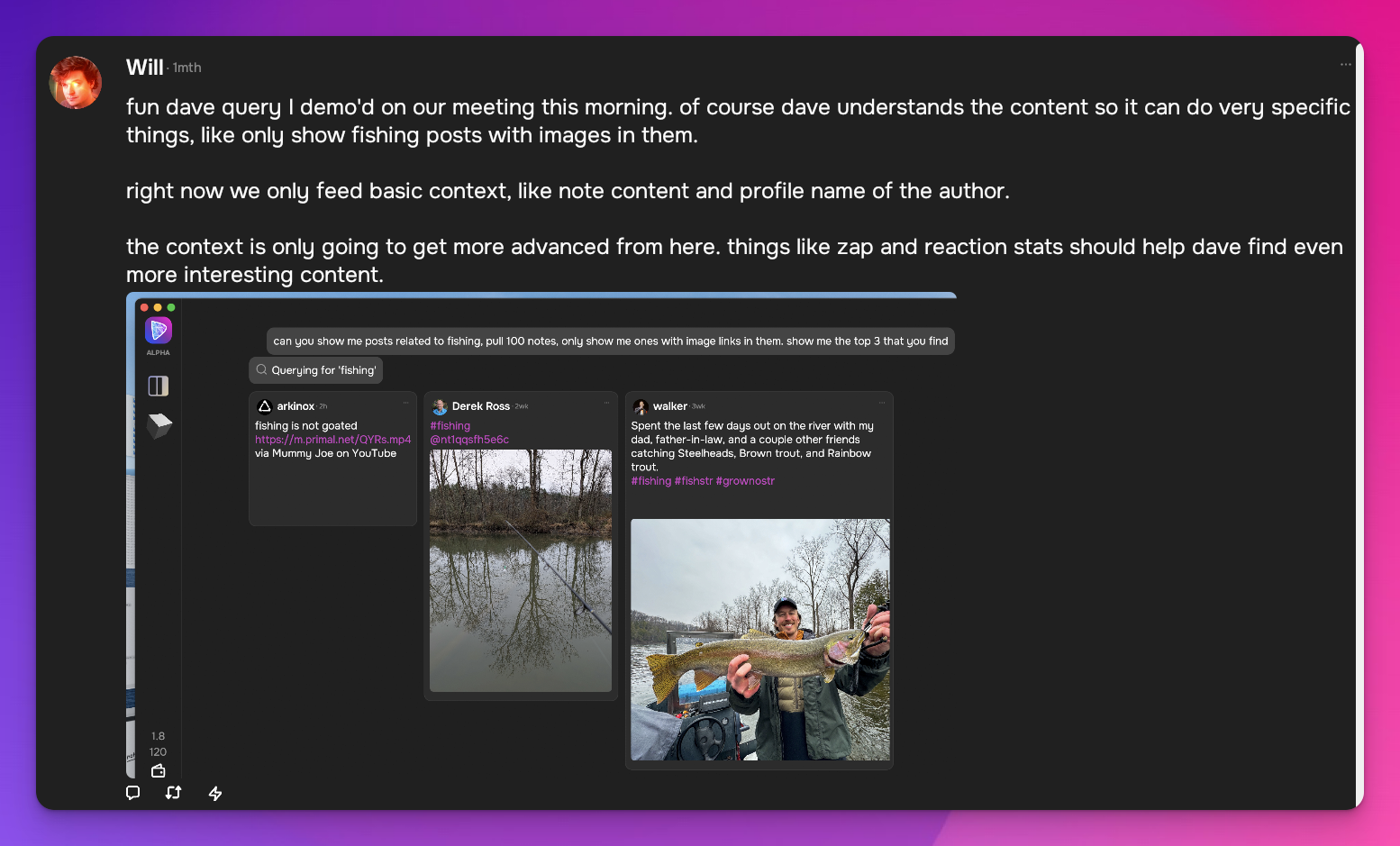
Search
The beta release includes a fulltext search interface powered by nostrdb:
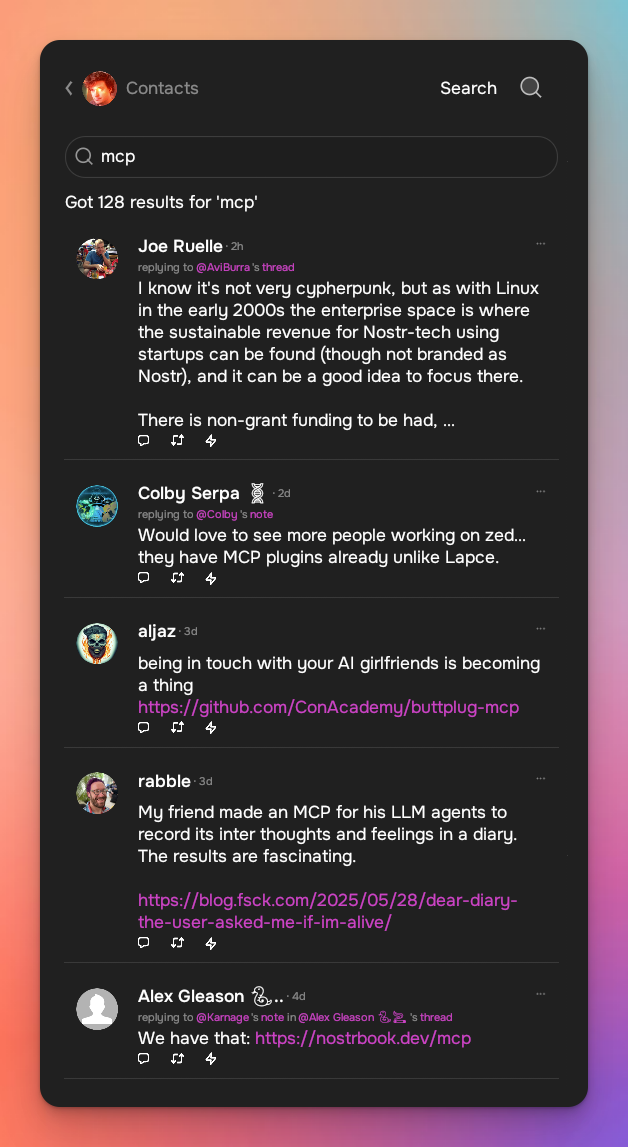
Zaps
You can now zap with NWC!
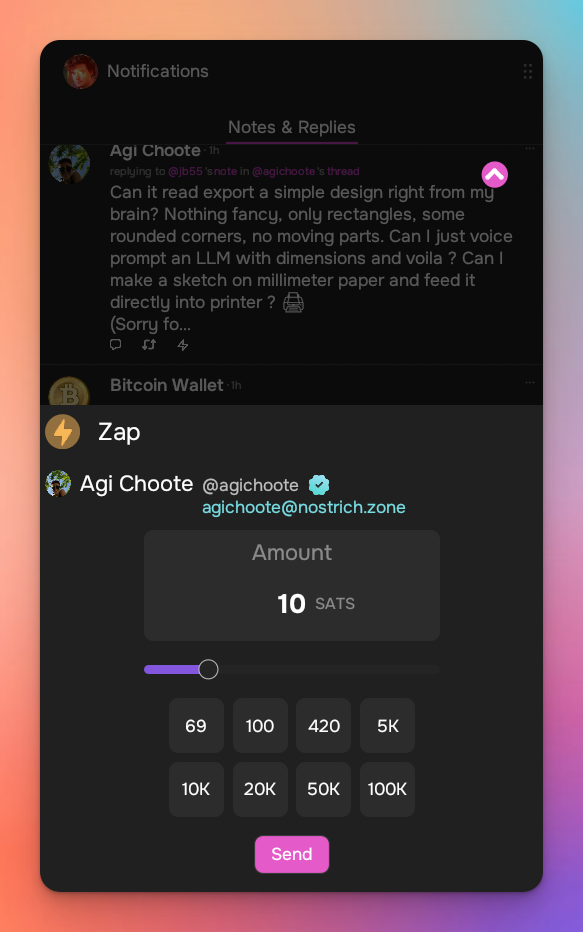
And More!
- GIFs!
- Add full screen images, add zoom & pan
- Introduce last note per pubkey feed (experimental)
- Allow multiple media uploads per selection
- Major Android improvements (still wip)
- Added notedeck app sidebar
- User Tagging
- Note truncation
- Local network note broadcast, broadcast notes to other notedeck notes while you're offline
- Mute list support (reading)
- Relay list support
- Ctrl-enter to send notes
- Added relay indexing (relay columns soon)
- Click hashtags to open hashtag timeline
Damus iOS
Work continued on the iOS side. While I was not directly involved in the work since the last report, I have been directing and managing its development.
What's new:
Coinos Wallet + Interface
We've partnered with coinos to enable a one-click, non-KYC lightning wallet!
We now have an NWC wallet interface, and we've re-enabled zaps as per the new appstore guidelines!
Now you can see all incoming and outgoing NWC transactions and start zapping right away.
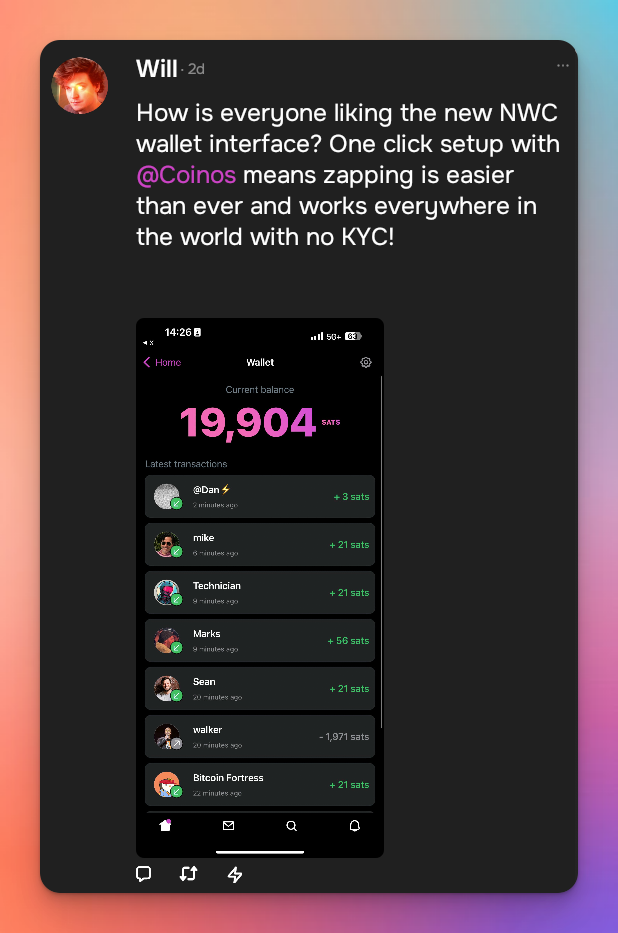
Enhanced hellthread muting
Damus can now automatically mute hellthreads, instead of having to do that manually.
Drafts
We now locally persist note drafts so that they aren't lost on app restart!
Profile editing enhancements
We now have a profile picture editing tool so that profile pictures are optimized and optionally cropped
Conversations tab
We now have a conversations tab on user profiles, allowing you to see all of your past conversations with that person!
Enhanced push notifications
We've updated our push notifications to include profile pictures, and they are also now grouped by the thread that they came from.
And lots more!
Too many to list here, check out the full changelog
Nostrdb
nostrdb, the engine that powers notecrumbs, damus iOS, and notedeck, continued to improve:
Custom filters
We've added the ability to include custom filtering logic during any nostrdb query. Dave uses this to filter replies from kind1 results to keep the results small and to avoid doing post-processing.
Relay index + queries
There is a new relay index! Now when ingesting notes, you can include extra metadata such as where the note came from. You can use this index to quickly list all of the relays for a particular note, or for relay timelines.
NIP50 profile searches
To assist dave in searching for profiles, we added a new query plan for {kind:0, search:} queries to scan the profile search index.
How money was used
- relay.damus.io server costs
- Living expenses
Next quarter
We're making a strong push to get our Android version released, so that is the main focus for me.
-
 @ fa0165a0:03397073
2025-06-01 12:23:47
@ fa0165a0:03397073
2025-06-01 12:23:47Test of untype
Let see what this markdown editor goes for. Quite nice layout, but so far in my testing only usable via computer. On phone, the keyboard covers the writing area, hehe. Now, where do these get published when posted?
-
 @ 8c29b321:4336aaa0
2025-06-05 08:32:10
@ 8c29b321:4336aaa0
2025-06-05 08:32:10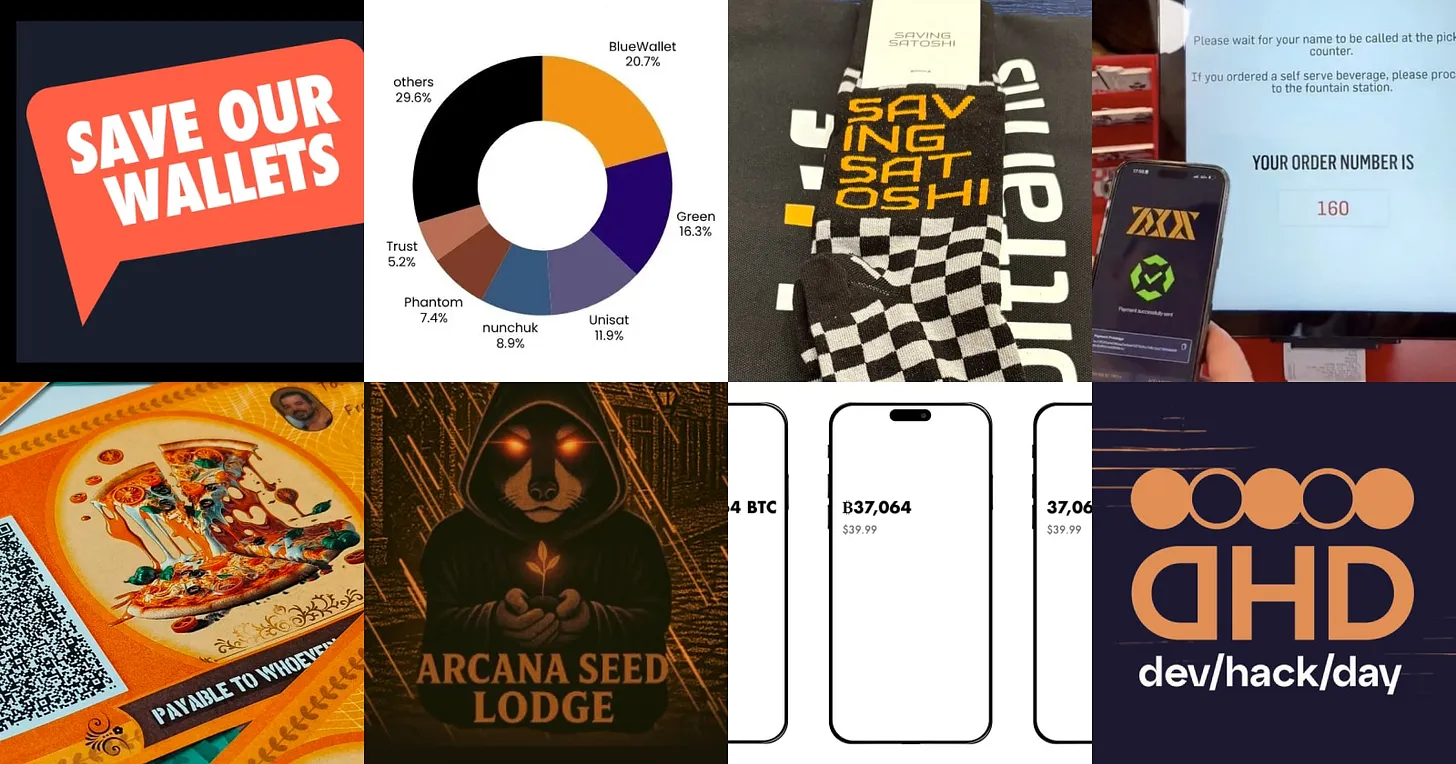
Community 🧑🤝🧑
- Did you see that the Designathon wrapped up? If not, take a peek at the previous newsletter.
- The community conducted research at Oslo Freedom Forum. Bitcoin and Nostr have the potential to provide privacy focussed financial and communication tools for activists. We'll publish findings publicly and host developer workshops to share the insights.
- BTC Prague is coming up from June 18 to 21. Meet up at the design track during dev/hack/day and around the general conference. The aforementioned activist research and Bitcoin Core App are two of the scheduled talks.
- We had an exploratory call about how Liana could implement Payjoins (recording).
- The price for Best Design at the Bitcoin 2025 hackathon, sponsored by the Bitcoin Design Foundation, went to Arcana Seed Lodge. Check out all the projects.
- For anyone in the US, help protect your right to transact freely via Save our Wallets. There’s a bill being discussed around protecting builders of non-custodial wallets and services.
Bitcoin design guide 🗺️
- The intro page to the Getting Started section got a rewrite. Does it read better and is it more informative now?
- The section for visual formatting of addresses was updated with a note about using fonts with clearly distinguishable characters.
- Find new t-shirt designs with bitcoin & design related taglines on the Design files page (Figma community file).
- Would you like to help create an online course around design for Plan₿ Network?
- AI knows the guide and can evaluate your design based on it. How else can we use AI?
Seeking feedback 🗣️👂
- Liana Wallet is interviewing bitcoiners around frustrations with self-custody.
- Yashraj is seeking feedback on UX challenges around Payjoin V2 (outline, Github, Stacker News).
- 0commons is a bitcoin-powered value-for-value marketplace for digital goods. Leave your feedback.
- Kelbs is looking for feedback on home screen designs for Sovrn.
- m1sterc001guy is looking for feedback on a Fedimint wallet prototype (repo).
- There is a lot of activity around bitcoin redenomination (BIP 177), removing the term satoshi as a unit. Join the conversation.
Wallet updates 👜
- An update on Cashu ecosystem developments in Q1 2025.
- Boardwalk Cash is an example for the redenomination of bitcoin units. A live example on how “1 Satoshi” can be displayed as “1 Bitcoin”.
- Wallet of Satoshi is going to release a non-custodial wallet and become available again in the US.
- Akron released a beta wallet with support for the Spaces protocol.
- Blockstream released a new wallet app.
- Sparrow made several accessibility improvements in the 2.2.0 release.
Conferences 📅
- Catch up with the recordings and hackathon winners of the BTC++ Austin conference.
- Watch presentations of the Bitcoin Presidio hackathon finalists.
- Find a more complete list of conferences here.
Opportunities 💡
- BRAIINS is looking for a content Lead.
- Apply to the Bitshala design fellowship.
- Cowbolt is looking for a designer.
Everything else 😀
- HRF is supporting another 22 projects with grants. Take a look.
- Happy Bitcoin Pizza Day!
- Check out Jason’s guide to bitcoin accessibility.
- View survey results around mobile wallet usage in Japan by Diamond Hands.
- The Second team published research around how the Ark network can complement Lightning infrastructure.
- Watch the Freedom Tech track presentations from the Oslo Freedom forum.
- Watch Daniel answer 21 questions in 21 minutes.
- Read Bitcoin testing is a ghost town by AVB (also part two).
- Saving Satoshi did a workshop at the Bitcoin Conference. Have you tried it?
- See the UX of paying for burgers at the US fast-food chain Steak’n Shake.
- A guidepr to Robosats, for private exchange of bitcoin.
- Hear about the latest on Fedimint in this podcast.
- Read about building inclusivity into every phase of a project.
- Check out the Global State of Crypto report by Gemini.
—
For more, visit the Bitcoin Design website and follow us.
This update is brought to you by Christoph & Mo. We’d love to hear your feedback. -
 @ d5c440ce:04726d89
2025-06-05 06:19:49
@ d5c440ce:04726d89
2025-06-05 06:19:49Effektiv behandling af blodsprængninger kræver en professionel tilgang og de rette metoder. Hos Klinik Zenit tilbyder vi skånsomme og dokumenterede teknikker til at reducere synligheden af blodsprængninger i ansigt og på krop. Vores behandlinger tilpasses individuelt og udføres af erfarne specialister med fokus på sikkerhed og langvarige resultater. Få vejledning om hudpleje før og efter behandlingen for at opnå det bedste resultat. Kontakt Klinik Zenit for en professionel vurdering og behandlingsplan.
-
 @ 31a4605e:cf043959
2025-06-05 13:03:59
@ 31a4605e:cf043959
2025-06-05 13:03:59Nos últimos anos, o Bitcoin tem sido frequentemente comparado ao ouro, ganhando o nome de "ouro digital". Essa comparação ocorre porque ambas as formas de valor têm características em comum, como escassez, durabilidade e aceitação mundial. Contudo, o Bitcoin também representa uma novidade tecnológica que muda a ideia de dinheiro e investimento, se destacando como uma alternativa moderna e eficaz ao ouro físico.
Uma das razões pelas quais o Bitcoin é comparado ao ouro é a sua escassez programada. Enquanto o ouro é um recurso natural limitado, cuja oferta depende da mineração, o Bitcoin tem um teto máximo de 21 milhões de unidades, definido em seu código. Esse teto faz com que o Bitcoin seja protegido contra a inflação, ao contrário das moedas tradicionais, que podem ser criadas sem limites pelos bancos centrais.
Essa característica traz um valor duradouro, parecido com o ouro, já que a oferta limitada ajuda a manter o poder de compra ao longo do tempo. Com o aumento da procura por Bitcoin, sua quantidade reduzida reforça seu papel como reserva de valor.
Outro aspecto que aproxima o Bitcoin do ouro é a durabilidade. Enquanto o ouro resiste à corrosão e pode ser guardado por séculos, o Bitcoin é um ativo digital protegido por criptografia avançada e armazenado na blockchain — um livro-razão imutável e descentralizado.
Além disso, o Bitcoin é mais fácil de transportar do que o ouro. Mover ouro físico envolve custos e segurança, tornando o transporte complicado, principalmente em transações internacionais. Por outro lado, o Bitcoin pode ser enviado digitalmente para qualquer parte do mundo em minutos, com taxas baixas e sem intermediários. Essa vantagem tecnológica torna o Bitcoin mais eficaz para um mundo globalizado e digital.
A segurança é outra característica que o Bitcoin e o ouro têm em comum. O ouro é difícil de falsificar, fazendo dele uma reserva de valor confiável. Da mesma forma, o Bitcoin usa protocolos de criptografia que asseguram transações seguras e protegidas contra fraudes.
Além disso, todas as transações feitas com Bitcoin são registradas na blockchain, fornecendo um nível de transparência que o ouro físico não oferece. Qualquer pessoa pode revisar as transações na rede, aumentando a confiança e a rastreabilidade.
EconômicaHistoricamente, o ouro tem sido utilizado como proteção contra a inflação e crises econômicas. Durante momentos de instabilidade, os investidores buscam o ouro como uma maneira de preservar seu patrimônio. O Bitcoin, por sua vez, está surgindo como uma alternativa digital com o mesmo propósito.
Em países com alta inflação ou instabilidade política, o Bitcoin tem sido usado como uma proteção contra a desvalorização das moedas locais. Sua natureza descentralizada impede que governos confisquem ou controlem diretamente o ativo, garantindo maior liberdade financeira para os usuários.
Apesar de suas semelhanças com o ouro, o Bitcoin ainda enfrenta desafios. Sua volatilidade é muito maior, o que pode causar incertezas a curto prazo. No entanto, muitos especialistas afirmam que essa volatilidade é uma característica comum em ativos novos e tende a diminuir com o tempo, à medida que a aceitação cresce e o mercado se desenvolve.
Outro desafio é a regulamentação. Enquanto o ouro já é reconhecido globalmente como um ativo financeiro, o Bitcoin ainda enfrenta resistência de governos e instituições financeiras, que procuram formas de controlá-lo e regulá-lo.
Resumindo, o Bitcoin, muitas vezes chamado de "ouro digital", oferece uma nova forma de valor que combina as melhores características do ouro com a eficiência e a inovação da tecnologia digital. Sua escassez planejada, segurança criptográfica, portabilidade e resistência à censura fazem dele uma alternativa viável para preservar riqueza e realizar transações no mundo moderno.
Mesmo com muita volatilidade, o Bitcoin está se firmando como uma reserva de valor e como um ativo de proteção contra crises econômicas. Assim, ele representa não apenas uma evolução do sistema financeiro, mas também um símbolo da mudança para uma economia digital descentralizada e global.
Muito obrigado por teres lido o texto até aqui, espero que esteja tudo bem contigo e um abraço enorme do teu madeirense bitcoiner maximalista favorito. Viva a liberdade!
-
 @ 45ea632c:bb0b4fa1
2025-06-05 08:01:04
@ 45ea632c:bb0b4fa1
2025-06-05 08:01:04No mundo do entretenimento digital, a inovação e a experiência do usuário são fatores determinantes para o sucesso de uma plataforma. A Win44 surge como uma das opções mais promissoras do mercado brasileiro, oferecendo uma experiência completa e diferenciada para quem busca diversão, praticidade e oportunidades de ganhos reais. Com uma interface moderna, variedade de jogos e suporte de alta qualidade, a Win44 tem se destacado entre as preferidas dos jogadores.
Uma Plataforma Moderna e Intuitiva Desde o primeiro acesso, a Win44 impressiona pelo seu design moderno, navegação fluida e compatibilidade com diferentes dispositivos. Seja no computador, tablet ou smartphone, a plataforma se adapta perfeitamente, garantindo uma experiência sem interrupções e totalmente otimizada.
Além da estética, a funcionalidade também chama atenção. Os menus são organizados de forma clara, facilitando a busca por jogos, promoções e informações da conta do usuário. Isso é ideal tanto para iniciantes quanto para jogadores mais experientes, que valorizam a praticidade no dia a dia.
Variedade de Jogos para Todos os Perfis Um dos grandes diferenciais da win44é a sua biblioteca de jogos, que abrange diferentes gostos e estilos. A plataforma conta com opções que vão desde os clássicos de mesa até os jogos de azar mais populares, todos desenvolvidos por fornecedores renomados da indústria.
Entre os destaques, estão os jogos de cartas como pôquer, bacará e blackjack, além de uma ampla seleção de jogos de roleta e máquinas de giros com diferentes temáticas e dinâmicas. Os gráficos são envolventes, com animações fluidas e efeitos sonoros que aumentam a imersão do jogador, proporcionando uma experiência realista e empolgante.
Outro ponto positivo é a presença de jogos ao vivo com crupiês reais, o que adiciona uma camada extra de emoção e interação, aproximando ainda mais o jogador da atmosfera dos grandes centros de entretenimento internacionais.
Experiência do Jogador em Primeiro Lugar A Win44 investe constantemente na qualidade do atendimento ao usuário e na segurança da plataforma. O suporte está disponível 24 horas por dia, todos os dias da semana, com atendimento em português e canais de fácil acesso, como chat ao vivo e e-mail.
No quesito segurança, a plataforma utiliza tecnologia de criptografia avançada para proteger todas as transações e dados dos usuários, garantindo total confidencialidade. Além disso, o processo de registro é simples e rápido, permitindo que o jogador comece a se divertir em poucos minutos.
Outro ponto muito valorizado pelos usuários é a variedade de métodos de pagamento e saque. A Win44 oferece suporte a diversas opções, incluindo transferências bancárias, carteiras digitais e até pagamentos via PIX, que têm ganhado grande popularidade no Brasil por sua rapidez e conveniência.
Bônus e Promoções Atrativas Para tornar a experiência ainda mais interessante, a Win44 oferece uma gama de promoções e bônus regulares. Novos usuários podem aproveitar ofertas de boas-vindas que aumentam o saldo inicial, enquanto jogadores frequentes têm acesso a promoções sazonais, sorteios e programas de fidelidade.
Essas vantagens não apenas elevam o nível da diversão, mas também aumentam as chances de obter bons resultados durante as partidas.
Conclusão A Win44 é uma plataforma completa que combina tecnologia, diversidade e um atendimento de excelência para proporcionar a melhor experiência de entretenimento online. Com um ambiente seguro, jogos variados e uma interface amigável, ela se consolida como uma das principais escolhas para jogadores brasileiros que buscam diversão de qualidade.
-
 @ bc575705:dba3ed39
2025-03-13 05:57:10
@ bc575705:dba3ed39
2025-03-13 05:57:10In our hyper-connected age, the concept of "Know Your Customer" (KYC) has morphed from a regulatory necessity into a pervasive surveillance apparatus, subtly eroding our fundamental liberties. While purported to combat financial crime, KYC has become a tool for mass surveillance, data exploitation, and the gradual dismantling of personal privacy. Let’s embark on a comprehensive exploration of this system, exposing its inherent flaws and advocating for a paradigm shift towards decentralized financial sovereignty.
Beyond the Surface: The Intricate Web of KYC Data Collection
KYC transcends mere identity verification; it's a deep dive into the minutiae of our lives. Consider the breadth and depth of data extracted:
Geographic Surveillance: Proof of address requirements delve into historical residency, creating granular maps of our movements. Combined with location data from mobile devices and online activity, this paints a comprehensive picture of our physical presence.
Financial Autopsy: KYC dissects our financial lives with surgical precision. Income sources, asset declarations, and transaction histories are meticulously cataloged. Algorithmic analysis reveals spending habits, investment strategies, and even potential political affiliations.
Behavioral Predictive Modeling: AI algorithms analyze our financial behavior, predicting future actions and preferences. This data is invaluable for targeted advertising, but also for social engineering and political manipulation.
Biometric Invasiveness: Facial recognition, iris scans, and voice analysis create permanent, immutable records of our physical selves. These biometrics are highly sensitive and vulnerable to breaches, potentially leading to identity theft and even physical harm.
Social Network Mapping: KYC extends beyond individuals, mapping our social and professional networks. Institutions analyze our connections, identifying potential risks based on our associations. This has a chilling effect on free association and dissent, as individuals become hesitant to associate with those deemed "risky."
Psychometric Profiling: With the increase of online tests, and the collection of online data, companies and states can build psychometric profiles. These profiles can be used to predict actions, and even manipulate populations.
The Fallacy of Security: KYC's Ineffectiveness and the Rise of the Surveillance State
Despite its claims, KYC fails to effectively combat sophisticated financial crime. Instead, it creates a system of mass surveillance that disproportionately targets law-abiding citizens.
The Scourge of False Positives: Automated KYC systems frequently generate false positives, flagging innocent individuals as potential criminals. This can lead to financial exclusion, reputational damage, and even legal persecution.
A Ticking Time Bomb: Centralized KYC databases are prime targets for hackers, putting vast amounts of sensitive personal information at risk. Data breaches can lead to identity theft, financial fraud, and even physical harm.
The State's Panopticon: KYC empowers governments to monitor the financial activities of their citizens, creating a powerful tool for surveillance and control. This can be used to suppress dissent, target political opponents, and enforce conformity.
The Criminals Advantage: Sophisticated criminals easily bypass KYC using shell companies, money laundering, and other techniques. This makes KYC a system that punishes the innocent, and gives the criminals a false sense of security for the data collected.
Decentralized Alternatives: Reclaiming Financial Sovereignty and Privacy
In the face of this encroaching surveillance state, decentralized technologies offer a path to financial freedom and privacy.
Cryptocurrency | A Bastion of Financial Freedom: Bitcoin and other cryptocurrencies provide censorship-resistant alternatives to traditional financial systems. They empower individuals to transact freely, without the need for intermediaries or government oversight.
Decentralized Finance (DeFi) | Democratizing Finance: DeFi platforms offer a range of financial services, including lending, borrowing, and trading, without the need for traditional banks. These platforms are built on blockchain technology, ensuring transparency, security, and accessibility.
Self-Sovereign Identity (SSI) | Empowering Individuals: SSI solutions enable individuals to control their own digital identities, without relying on centralized authorities. This allows for secure and private verification of identity, without the need to share sensitive personal information with every service provider.
Privacy-Enhancing Technologies (PETs) | Shielding Your Data: Technologies like zero-knowledge proofs, homomorphic encryption, and secure multi-party computation can be used to protect personal data while still allowing for necessary verification.
Decentralized Autonomous Organizations (DAOs) | Creating new forms of governance: DAOs provide new ways for groups to organize, and make decisions. They provide a transparent way to pool resources, and make decisions.
A Call to Action: Defending Our Digital Rights and Building a Decentralized Future
We cannot passively accept the erosion of our fundamental freedoms. We must actively defend our digital rights and demand a more just and equitable financial system.
Advocate for Robust Privacy Laws: Demand stronger regulations that limit the collection and use of personal data.
Champion Decentralized Technologies: Support the development and adoption of cryptocurrencies, DeFi platforms, and other decentralized solutions.
Educate and Empower: Raise awareness about the dangers of KYC and state surveillance.
Cultivate Critical Thinking: Question the narratives presented by governments and corporations.
Build Decentralized Communities: Join and support decentralized communities that are working to build a more free and open financial system.
Demand transparency from all data collection: Insist that all data collection is open, and that there are strong penalties for those that misuse data.
The fight for financial freedom is a fight for human freedom. Let us stand together and reclaim our digital sovereignty.
-
 @ cae03c48:2a7d6671
2025-06-03 19:02:12
@ cae03c48:2a7d6671
2025-06-03 19:02:12Bitcoin Magazine

Sberbank, Russia’s Biggest Bank, Launches Structured Bond Tied to BitcoinSberbank, the largest bank in Russia, has launched a new structured bond that ties investor returns to the performance of Bitcoin and the U.S. dollar-to-ruble exchange rate. This new financial product represents one of the first moves by a major Russian institution to offer Bitcoin-linked investments under recently updated national regulations.
BREAKING:
 Russia's largest bank Sberbank launches structured bonds linked to Bitcoin. pic.twitter.com/LtD26jPS0x
Russia's largest bank Sberbank launches structured bonds linked to Bitcoin. pic.twitter.com/LtD26jPS0x— Bitcoin Magazine (@BitcoinMagazine) June 2, 2025
The structured bond is initially available over the counter to a limited group of qualified investors. According to the announcement, it allows investors to earn based on two factors: the price performance of BTC in U.S. dollars and any strengthening of the dollar compared to the Russian ruble.
Unlike typical Bitcoin investments, this product does not require the use of a Bitcoin wallet or foreign platforms. “All transactions [are] processed in rubles within Russia’s legal and infrastructure systems,” Sberbank stated, highlighting compliance with domestic financial protocols.
In addition to the bond, Sberbank has announced plans to launch similar structured investment products with Bitcoin exposure on the Moscow Exchange. The bank also revealed it will introduce a Bitcoin futures product via its SberInvestments platform on June 4, aligning with the product’s debut on the Moscow Exchange.
These developments follow a recent policy change by the Bank of Russia, which now permits financial institutions to offer Bitcoin-linked instruments to qualified investors. This shift opens the door for Bitcoin within the country’s traditional financial markets.
While Russia has previously taken a cautious approach to digital assets, Sberbank’s launch of a Bitcoin-linked bond and upcoming futures product marks a new phase of adoption—one that blends Bitcoin exposure with existing financial infrastructure.
The bank’s structured bond may signal a growing interest in regulated access to Bitcoin, especially within large financial institutions.
This post Sberbank, Russia’s Biggest Bank, Launches Structured Bond Tied to Bitcoin first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ 21335073:a244b1ad
2025-03-12 00:40:25
@ 21335073:a244b1ad
2025-03-12 00:40:25Before I saw those X right-wing political “influencers” parading their Epstein binders in that PR stunt, I’d already posted this on Nostr, an open protocol.
“Today, the world’s attention will likely fixate on Epstein, governmental failures in addressing horrific abuse cases, and the influential figures who perpetrate such acts—yet few will center the victims and survivors in the conversation. The survivors of Epstein went to law enforcement and very little happened. The survivors tried to speak to the corporate press and the corporate press knowingly covered for him. In situations like these social media can serve as one of the only ways for a survivor’s voice to be heard.
It’s becoming increasingly evident that the line between centralized corporate social media and the state is razor-thin, if it exists at all. Time and again, the state shields powerful abusers when it’s politically expedient to do so. In this climate, a survivor attempting to expose someone like Epstein on a corporate tech platform faces an uphill battle—there’s no assurance their voice would even break through. Their story wouldn’t truly belong to them; it’d be at the mercy of the platform, subject to deletion at a whim. Nostr, though, offers a lifeline—a censorship-resistant space where survivors can share their truths, no matter how untouchable the abuser might seem. A survivor could remain anonymous here if they took enough steps.
Nostr holds real promise for amplifying survivor voices. And if you’re here daily, tossing out memes, take heart: you’re helping build a foundation for those who desperately need to be heard.“
That post is untouchable—no CEO, company, employee, or government can delete it. Even if I wanted to, I couldn’t take it down myself. The post will outlive me on the protocol.
The cozy alliance between the state and corporate social media hit me hard during that right-wing X “influencer” PR stunt. Elon owns X. Elon’s a special government employee. X pays those influencers to post. We don’t know who else pays them to post. Those influencers are spurred on by both the government and X to manage the Epstein case narrative. It wasn’t survivors standing there, grinning for photos—it was paid influencers, gatekeepers orchestrating yet another chance to re-exploit the already exploited.
The bond between the state and corporate social media is tight. If the other Epsteins out there are ever to be unmasked, I wouldn’t bet on a survivor’s story staying safe with a corporate tech platform, the government, any social media influencer, or mainstream journalist. Right now, only a protocol can hand survivors the power to truly own their narrative.
I don’t have anything against Elon—I’ve actually been a big supporter. I’m just stating it as I see it. X isn’t censorship resistant and they have an algorithm that they choose not the user. Corporate tech platforms like X can be a better fit for some survivors. X has safety tools and content moderation, making it a solid option for certain individuals. Grok can be a big help for survivors looking for resources or support! As a survivor, you know what works best for you, and safety should always come first—keep that front and center.
That said, a protocol is a game-changer for cases where the powerful are likely to censor. During China's # MeToo movement, survivors faced heavy censorship on social media platforms like Weibo and WeChat, where posts about sexual harassment were quickly removed, and hashtags like # MeToo or "woyeshi" were blocked by government and platform filters. To bypass this, activists turned to blockchain technology encoding their stories—like Yue Xin’s open letter about a Peking University case—into transaction metadata. This made the information tamper-proof and publicly accessible, resisting censorship since blockchain data can’t be easily altered or deleted.
I posted this on X 2/28/25. I wanted to try my first long post on a nostr client. The Epstein cover up is ongoing so it’s still relevant, unfortunately.
If you are a survivor or loved one who is reading this and needs support please reach out to: National Sexual Assault Hotline 24/7 https://rainn.org/
Hours: Available 24 hours
-
 @ 49d472c1:a63cd544
2025-06-05 02:59:12
@ 49d472c1:a63cd544
2025-06-05 02:59:12Bitcoin Miners Pivot to Power AI Boom, Offering a Lifeline to America’s Data-Center Crunch
A fresh Morgan Stanley analysis warns that U.S. data-center demand will balloon to ≈65 GW between 2025 and 2028—about 45 GW more than the grid can currently supply. One solution the bank singles out: repurposing the oversized, transformer-fed campuses originally built for Bitcoin mining. (investopedia.com)
Several public miners are already moving. Riot Platforms has begun buying extra land near its Corsicana, TX complex and hired a veteran data-center executive to head a “high-performance compute” division aimed squarely at AI customers. (riotplatforms.com, coindesk.com) Bitfarms, meanwhile, is marketing North-American sites to hyperscalers after hiring consultants to evaluate GPU-ready retrofits. (reuters.com)
Industry analysts say the pivot is existential. April 2024’s fourth halving chopped block rewards to 3.125 BTC, shrinking miner revenue just as network difficulty hit record highs. By leasing idle megawatts—or fully converting halls—operators lock in dollar-denominated cash-flows while retaining the option to resume mining if margins rebound.
“Miners spent the last cycle amassing land, switchgear and transformers. AI is about to pay them for it.” —Greg Miller, Citizens JMP (research note quoted in multiple sector briefings)
Why it matters
- Grid relief: Every gigawatt shifted from speculative hashing to AI compute eases ERCOT’s peak-load stress and shortens transmission-upgrade timelines. (datacenterdynamics.com)
- Cap-ex savings for cloud firms: Retrofitting a mining hall is months faster—and currently 30-40 % cheaper—than green-field construction, analysts estimate. (govtech.com)
- Dual-revenue model: Miners keep upside to future BTC price spikes while monetizing power capacity today.
The roadblocks
- Cooling retrofits: Air-cooled ASIC barns must be re-engineered for liquid-cooled GPU clusters, at up to \$3 M per MW in conversion costs. (driehaus.com)
- Policy risk in Texas: Lawmakers are weighing caps on industrial load-flex credits after recent grid-stress events, which could dent miners’ ancillary revenue. (dallasnews.com)
Bottom line: Once-beleaguered Bitcoin mines may become critical real estate for the surging AI sector—turning yesterday’s crypto boomtowns into tomorrow’s compute hubs while giving miners a much-needed new income stream.
-
 @ 812cff5a:5c40aeeb
2025-06-05 12:55:10
@ 812cff5a:5c40aeeb
2025-06-05 12:55:10Chorus: تجربة في البرمجة الانسداحية
كيفية بناء تطبيق Nostr بسرعة البرق باستخدام الذكاء الاصطناعي.
في 26 مايو، تم إطلاق تطبيق Chorus في منتدى أوسلو للحرية. صُمم هذا التطبيق للناشطين والمعارضين ومنظمي المجتمع، ويتميز بمجموعات تشبه تلك الموجودة في فيسبوك مع محفظة eCash مدمجة لجمع التبرعات.
Chorus مبني على Nostr، وهو بروتوكول لامركزي ومفتوح مصمم ليكون مقاومًا للرقابة. يمكن لأي شخص في العالم إنشاء حساب Nostr والنشر إلى خوادم Nostr، أو حتى بناء تطبيق Nostr خاص به — ولا يمكن لأحد إيقافه. هذا ما يجعل Nostr المكان المثالي للمقاتلين من أجل الحرية، الذين غالبًا ما يواجهون الرقابة من الحكومات الاستبدادية أو الشركات التي تتحكم في المنصات الاجتماعية الرئيسية.
يمكن للمستخدمين إنشاء حساب Chorus (أو تسجيل الدخول باستخدام حساب Nostr موجود) في ثوانٍ والبدء فورًا في استلام eCash، وإنشاء مجموعات، ومشاركة المحتوى. يتضمن التطبيق ميزات قوية لإدارة المجتمع، بحيث يمكن للمجموعات اختيار أنواع المحتوى التي تسمح بها وفقًا لشروطها الخاصة. يمكن للمستخدمين إرسال eCash على الفور إلى المجموعات التي يرغبون في دعمها، مما يوفر أداة لجمع التبرعات عبر الحدود لا يمكن لأي حكومة إيقافها.
قبل عام فقط، ربما استغرق بناء النسخة التي تم إطلاقها الأسبوع الماضي من Chorus أسابيع. ولكن بفضل أدوات الذكاء الاصطناعي الحالية، قمنا بذلك في خمسة أيام فقط.
⸻
كيفية القيام بذلك: بناء تطبيق في أيام باستخدام وكلاء الذكاء الاصطناعي
الخطوة 1: تجميع الفريق
تم بناء Chorus بواسطة And Other Stuff، وهي مجموعة جديدة مكرسة لتعزيز Nostr في خمسة مجالات رئيسية: تجربة المستخدم والتسجيل، المجتمعات، الاتصالات الخاصة، التجارة، والذكاء الاصطناعي. شمل فريق هذا المشروع: • Calle، منشئ Cashu (eCash) • JeffG، منشئ White Noise (الاتصالات الخاصة) • Rabble و Liz Swiegart من Nos (تجربة المستخدم والتسجيل) • Alex Gleason و MK Fain، منشئو Soapbox (المجتمعات) • و Jack Dorsey (مستشار)
الخطوة 2: البدء بقالب قوي
عند البرمجة بالانسداح، السياق هو الملك. إذا بدأت بمجلد فارغ وطلبت من وكيل ذكاء اصطناعي “بناء تطبيق مجموعات Nostr”، فلا يزال أمامك الكثير من العمل للحصول على شيء وظيفي حتى بشكل بسيط. من المحتمل أن تكون تنفيذات Nostr محاكاة، لا تتصل بخوادم حقيقية، أو تم تنفيذها بشكل غير صحيح. قد تكون أنواع الأحداث خاطئة، وقد لا يتم تحميل واجهة المستخدم، وحظًا سعيدًا في محاولة معرفة الخطوة التالية لإصلاح الفوضى.
هذا لأن الذكاء الاصطناعي يفتقر إلى بعض السياقات الرئيسية للبدء: • وثائق صديقة للذكاء الاصطناعي حول بروتوكول Nostr • أمثلة عالية الجودة على تنفيذ Nostr • أساسيات حول تكديس التكنولوجيا المفضل • سياق حول كيفية بناء المشروع وتشغيله وتصحيحه
الحل هو توفير المزيد من السياق، وسيكون العديد من مبرمجي الانسداح المخضرمين على دراية بالصراع في محاولة جعل الوكيل يقرأ روابط مختلفة للوثائق ويتبع 500 كلمة من السياق المصاغ بعناية في مطالبتهم الافتتاحية. ومع ذلك، غالبًا ما يربك هذا الوكلاء الذين يعملون بشكل أفضل مع مطالبات بسيطة. الحل لهذه المشكلة هو Stacks.
Stacks: بدء البرمجة الانسداحية بسرعة
Stacks تحل مشكلة نقص السياق الأولي من خلال إنشاء قوالب جاهزة مصممة خصيصًا لاستخدام وكلاء الذكاء الاصطناعي. يمكن استخدام “stack” لبناء أي نوع من المشاريع بأي لغة برمجة مع أي هدف نهائي في الاعتبار. بالنسبة لـ Chorus، استخدمنا MKStack، وهو قالب مصمم خصيصًا لبناء تطبيقات Nostr.
يتميز MKStack بعدة حلول للمشاكل الشائعة في الذكاء الاصطناعي: • Nostrbook MCP للاستعلام عن وثائق Nostr • مكونات بداية لميزات Nostr الشائعة مثل تسجيل الدخول • دعم Blossom لتحميل الوسائط • ملفات سياقية لتوجيه الوكيل خلال العقبات الشائعة وسير عمل التصحيح • نشر موقعك على الفور باستخدام Surge
النتيجة هي موقع جميل يعمل مباشرة مع Nostr في مطالبة واحدة:
“بناء تطبيق مجموعات على غرار فيسبوك على Nostr باستخدام NIP 72.”
كان هذا هو نتيجة تلك المطالبة الواحدة: http://groups72.surge.sh
الخطوة 3: إضافة الميزات باستخدام وكلاء الذكاء الاصطناعي
Stacks بدأت تطوير Chorus بسرعة. بعد ذلك، استخدمنا وكلاء الذكاء الاصطناعي لإضافة ميزات إضافية مثل: • محفظة eCash مدمجة • ميزات إدارة المجتمع • دعم الوسائط المتعددة
كل ذلك تم باستخدام مطالبات بسيطة وتوجيهات للذكاء الاصطناعي، مما سمح لنا ببناء تطبيق كامل الوظائف في أيام قليلة فقط.
⸻
ملاحظة:تم استخدام مصطلح برمجة الانسداحية بهدف الطرفة كترجمة لمصطلح Vibe coding تم كتابة هذه المقال من قبل المبدعة nostr: npub1jvnpg4c6ljadf5t6ry0w9q0rnm4mksde87kglkrc993z46c39axsgq89sc
-
 @ 94c2fd25:4fb53087
2025-06-05 06:41:55
@ 94c2fd25:4fb53087
2025-06-05 06:41:55EV8 không chỉ đơn thuần là một nền tảng cung cấp dịch vụ đa dạng mà còn là một biểu tượng của phong cách sống hiện đại, thuận tiện và thân thiện với môi trường. Với giao diện thân thiện và quy trình đăng ký, xác thực nhanh chóng, EV8 mang đến cho người dùng một trải nghiệm dễ dàng, giúp họ tiết kiệm thời gian trong cuộc sống bận rộn ngày nay. Các tính năng hỗ trợ thanh toán đa dạng như chuyển khoản ngân hàng, ví điện tử, và thẻ quốc tế tạo điều kiện thuận lợi cho mọi đối tượng sử dụng. Điều này góp phần thay đổi thói quen tiêu dùng của người dùng, từ những hành động đơn giản như nạp tiền, rút tiền, cho đến việc lựa chọn các dịch vụ phù hợp với nhu cầu cá nhân. EV8 giúp người dùng tiếp cận công nghệ một cách nhẹ nhàng, loại bỏ những trở ngại truyền thống, qua đó thúc đẩy sự phát triển của một xã hội số năng động và hiệu quả hơn.
Không chỉ tập trung vào tiện ích cá nhân, EV8 còn đóng vai trò quan trọng trong việc xây dựng cộng đồng bền vững và kết nối. Qua các chương trình ưu đãi, sự kiện hấp dẫn và hệ thống hỗ trợ khách hàng chuyên nghiệp, EV8 tạo nên sự gắn kết giữa người dùng và nền tảng, giúp họ cảm thấy được đồng hành và hỗ trợ mọi lúc mọi nơi. Những tính năng thông minh như quản lý năng lượng, theo dõi hoạt động và nhận thưởng qua các trò chơi cũng góp phần nâng cao nhận thức về sự cân bằng giữa giải trí và trách nhiệm trong cuộc sống. Từ đó, EV8 không chỉ là công cụ hỗ trợ mà còn là nguồn cảm hứng thúc đẩy người dùng sống chủ động, tích cực và thân thiện với môi trường trong kỷ nguyên số hóa ngày nay.
-
 @ 5d4b6c8d:8a1c1ee3
2025-06-05 01:28:52
@ 5d4b6c8d:8a1c1ee3
2025-06-05 01:28:52How did the stackers do on their ~HealthAndFitness journeys today?
I did very well: Slept well? Check Stuck to fast? Check Ate healthy? Check Activity target? Checkarooni
The one oddity I need to work on is that I got a foot cramp while playing turtle tag with my daughter.
https://stacker.news/items/997476
-
 @ 31a4605e:cf043959
2025-06-05 12:49:36
@ 31a4605e:cf043959
2025-06-05 12:49:36O surgimento do Bitcoin trouxe uma nova visão para o conceito de dinheiro, desafiando o sistema financeiro convencional baseado em moedas fiduciárias. Enquanto as moedas fiduciárias, como o real, o dólar e o euro, são amplamente usadas e reconhecidas como métodos de troca, o Bitcoin representa uma inovação digital que propõe descentralização e autonomia financeira. Embora ambos desempenhem funções básicas como meio de troca e reserva de valor, suas diferenças principais estão na maneira como são emitidos, geridos e transacionados.
Uma das principais distinções entre o Bitcoin e as moedas fiduciárias é a maneira como são emitidos e administrados. As moedas fiduciárias são emitidas por bancos centrais, que têm o poder de regular sua quantidade em circulação. Esse modelo permite a aplicação de políticas monetárias, como o aumento da oferta de dinheiro para estimular a economia ou a diminuição para controlar a inflação. No entanto, essa capacidade também pode resultar na desvalorização da moeda, se for emitida em excesso.
O Bitcoin, por outro lado, tem um sistema de emissão totalmente descentralizado. Ele é criado por meio de um processo chamado mineração, no qual computadores resolvem problemas matemáticos complexos para validar transações na rede. Além disso, a oferta total de bitcoins é limitada a 21 milhões de unidades, tornando-o um ativo deflacionário, ou seja, sua escassez pode aumentar seu valor ao longo do tempo. Essa limitação contrasta fortemente com a natureza ilimitada da impressão de moedas fiduciárias.
Moedas fiduciárias são centralizadas, o que significa que sua emissão e controle são decididos por autoridades governamentais. Isso também implica que transações feitas com essas moedas passam por intermediários, como bancos, que podem aplicar taxas e limites, além de estarem sujeitos a regulamentações e auditorias.
O Bitcoin, por sua vez, é descentralizado. Ele opera em uma rede peer-to-peer, onde as transações são verificadas por participantes chamados mineradores e registradas em um livro público conhecido como blockchain. Essa descentralização elimina a necessidade de intermediários, tornando o Bitcoin mais resistente à censura e ao controle governamental. Isso também proporciona maior transparência, já que qualquer pessoa pode verificar as transações na rede.
Outra diferença importante está na maneira como as transações são feitas. Com moedas fiduciárias, as transações geralmente dependem de bancos ou sistemas de pagamento, que podem impor restrições de horários e taxas altas, especialmente para transferências internacionais.
O Bitcoin, por outro lado, permite transferências diretas entre pessoas, em qualquer lugar do mundo e a qualquer momento, sem a necessidade de intermediários. Isso torna o sistema mais acessível, especialmente para aqueles que não possuem contas bancárias ou vivem em países com sistemas financeiros restritivos. Além disso, as taxas de transação do Bitcoin podem ser menores do que as taxas cobradas por bancos tradicionais.
As moedas fiduciárias proporcionam segurança baseada em leis governamentais e no sistema bancário, mas os usuários precisam confiar nesses intermediários. O Bitcoin, em contrapartida, oferece um alto nível de segurança através de criptografia avançada. As carteiras digitais, que guardam bitcoins, são protegidas por chaves privadas, assegurando que somente o dono possa acessá-las.
No entanto, a privacidade funciona de maneira diferente. Transações em moedas fiduciárias normalmente estão ligadas à identidade do usuário, enquanto o Bitcoin oferece um certo nível de anonimato, já que os endereços das carteiras não requerem identificação pessoal. Ainda assim, todas as transações são públicas e registradas no blockchain, o que pode ser um ponto de monitoramento para autoridades.
O valor das moedas fiduciárias é sustentado pela confiança no governo que as emite e na economia do país. Por outro lado, o Bitcoin não é apoiado por nenhum governo ou ativo físico. Seu valor é definido pela oferta e demanda no mercado, fazendo com que seja altamente volátil. Embora essa volatilidade apresente um risco, também atrai pessoas que veem o Bitcoin como uma possibilidade de valorização a longo prazo.
Resumindo, o Bitcoin e as moedas fiduciárias diferem significativamente em sua estrutura, controle e funcionalidade. Enquanto as moedas fiduciárias são controladas por governos e dependem de intermediários, o Bitcoin oferece descentralização, transparência e liberdade financeira. Apesar de sua volatilidade e alguns desafios relacionados à regulamentação, o Bitcoin representa uma alternativa nova ao sistema financeiro tradicional.
Muito obrigado por teres lido o texto até aqui, espero que esteja tudo bem contigo e um abraço enorme do teu madeirense bitcoiner maximalista favorito. Viva a liberdade!