-
 @ 21335073:a244b1ad
2025-05-09 13:56:57
@ 21335073:a244b1ad
2025-05-09 13:56:57Someone asked for my thoughts, so I’ll share them thoughtfully. I’m not here to dictate how to promote Nostr—I’m still learning about it myself. While I’m not new to Nostr, freedom tech is a newer space for me. I’m skilled at advocating for topics I deeply understand, but freedom tech isn’t my expertise, so take my words with a grain of salt. Nothing I say is set in stone.
Those who need Nostr the most are the ones most vulnerable to censorship on other platforms right now. Reaching them requires real-time awareness of global issues and the dynamic relationships between governments and tech providers, which can shift suddenly. Effective Nostr promoters must grasp this and adapt quickly.
The best messengers are people from or closely tied to these at-risk regions—those who truly understand the local political and cultural dynamics. They can connect with those in need when tensions rise. Ideal promoters are rational, trustworthy, passionate about Nostr, but above all, dedicated to amplifying people’s voices when it matters most.
Forget influencers, corporate-backed figures, or traditional online PR—it comes off as inauthentic, corny, desperate and forced. Nostr’s promotion should be grassroots and organic, driven by a few passionate individuals who believe in Nostr and the communities they serve.
The idea that “people won’t join Nostr due to lack of reach” is nonsense. Everyone knows X’s “reach” is mostly with bots. If humans want real conversations, Nostr is the place. X is great for propaganda, but Nostr is for the authentic voices of the people.
Those spreading Nostr must be so passionate they’re willing to onboard others, which is time-consuming but rewarding for the right person. They’ll need to make Nostr and onboarding a core part of who they are. I see no issue with that level of dedication. I’ve been known to get that way myself at times. It’s fun for some folks.
With love, I suggest not adding Bitcoin promotion with Nostr outreach. Zaps already integrate that element naturally. (Still promote within the Bitcoin ecosystem, but this is about reaching vulnerable voices who needed Nostr yesterday.)
To promote Nostr, forget conventional strategies. “Influencers” aren’t the answer. “Influencers” are not the future. A trusted local community member has real influence—reach them. Connect with people seeking Nostr’s benefits but lacking the technical language to express it. This means some in the Nostr community might need to step outside of the Bitcoin bubble, which is uncomfortable but necessary. Thank you in advance to those who are willing to do that.
I don’t know who is paid to promote Nostr, if anyone. This piece isn’t shade. But it’s exhausting to see innocent voices globally silenced on corporate platforms like X while Nostr exists. Last night, I wondered: how many more voices must be censored before the Nostr community gets uncomfortable and thinks creatively to reach the vulnerable?
A warning: the global need for censorship-resistant social media is undeniable. If Nostr doesn’t make itself known, something else will fill that void. Let’s start this conversation.
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ 57c631a3:07529a8e
2025-04-07 13:17:50
@ 57c631a3:07529a8e
2025-04-07 13:17:50What is Growth Engineering? Before we start: if you’ve already filled out the What is your tech stack? survey: thank you! If you’ve not done so, your help will be greatly appreciated. It takes 5-15 minutes to complete. Those filling out will receive results before anyone else, and additional analysis from myself and Elin. Fill out this survey here.**
npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m
Growth engineering was barely known a decade ago, but today, most scaleups and many publicly traded tech companies have dedicated growth teams staffed by growth engineers. However, some software engineers are still suspicious of this new area because of its reputation for hacky code with little to no code coverage.
For this reason and others, I thought it would be interesting to learn more from an expert who can tell us all about the practicalities of this controversial domain. So I turned to Alexey Komissarouk, who’s been in growth engineering since 2016, and was in charge of it at online education platform, MasterClass. These days, Alexey lives in Tokyo, Japan, where he advises on growth engineering and teaches the Growth Engineering course at Reforge.
In today’s deep dive, Alexey covers:
- What is Growth Engineering? In the simplest terms: writing code to help a company make more money. But there are details to consider: like the company size where it makes sense to have a dedicated team do this.
- What do Growth Engineers work on? Business-facing work, empowerment and platform work are the main areas.
- Why Growth Engineers move faster than Product Engineers. Product Engineers ship to build: Growth Engineers ship to learn. Growth Engineers do take shortcuts that would make no sense when building for longevity – doing this on purpose.
- Tech stack. Common programming languages, monitoring and oncall, feature flags and experimentation, product analytics, review apps, and more.
- What makes a good Growth Engineer? Curiosity, “build to learn” mindset and a “Jack of all trades” approach.
- Where do Growth Engineers fit in? Usually part of the engineering department, either operating as with an “owner” or a “hitchiker” model.
- Becoming a Growth Engineer. A great area if you want to eventually become a founder or product manager – but even if not, it can accelerate your career growth. Working in Growth forces you to learn more about the business.
With that, it’s over to Alexey:
I’ll never forget the first time I made my employer a million dollars.
I was running a push notification A/B test for meal delivery startup Sprig, trying to boost repeat orders.
A push notification similar to what we tested to boost repeat orders
Initial results were unpromising; the push notification was not receiving many opens. Still, I wanted to be thorough: before concluding the idea was a failure, I wrote a SQL query to compare order volume for subsequent weeks between customers in test vs control.
The SQL used to figure out the push notification’s efficiency
As it turned out, our test group “beat” the control group by around 10%:
‘review_5_push’ was the new type of push notification. Roughly the same amount of users clicked it, but they placed 10% more in orders
I plugged the numbers into a significance calculator, which showed it was statistically significant – or “stat-sig” – and therefore highly unlikely to be a coincidence. This meant we had a winner on our hands! But how meaningful was it, really, and what would adding the push notification mean for revenue, if rolled out to 100% of users?
It turned out this experiment created an additional $1.5 million dollars, annually, with just one push notification. Wow!
I was hooked. Since that day, I've shipped hundreds of experimental “winners” which generated hundreds of millions of incremental revenue for my employers. But you never forget the first one. Moments like this is what growth engineering is all about.
1. What is Growth Engineering?
Essentially, growth engineering is the writing of code to make a company money. Of course, all code produced by a business on some level serves this purpose, but while Product Engineers focus on creating a Product worth paying for, Growth Engineers instead focus on making that good product have a good business. To this end, they focus on optimizing and refining key parts of the customer journey, such as:
- Getting more people to consider the product
- Converting them into paying customers
- Keeping them as customers for longer, and spending more
What kinds of companies employ Growth Engineers? Places you’ve heard of, like Meta, LinkedIn, DoorDash, Coinbase, and Dropbox, are some of the ones I’ve had students from. There’s also OpenAI, Uber, Tiktok, Tinder, Airbnb, Pinterest… the list of high-profile companies goes on. Most newer public consumer companies you’ve heard have a growth engineering org, too.
Typically, growth engineering orgs are started by companies at Series B stage and beyond, so long as they are selling to either consumers or businesses via SaaS. These are often places trying to grow extremely fast, and have enough software engineers that some can focus purely on growth. Before the Series B stage, a team is unlikely to be ready for growth for various reasons; likely that it hasn’t found product-market fit, or has no available headcount, or lacks the visitor traffic required to run A/B tests.
Cost is a consideration. A fully-loaded growth team consisting of a handful of engineers, a PM, and a designer costs approximately 1 million dollars annually. To justify this, a rule of thumb is to have at least $5 million dollars in recurring revenue – a milestone often achieved at around the Series B stage.
Despite the presence of growth engineering at many public consumer tech companies, the field itself is still quite new, as a discipline and as a proper title.
Brief history of growth engineering
When I joined Opendoor in 2016, there was a head of growth but no dedicated growth engineers, but there were by the time I left in 2020. At MasterClass soon after, there was a growth org and a dozen dedicated growth engineers. So when did growth engineering originate?
The story is that its origins lie at Facebook in 2007. The team was created by then-VP of platform and monetization Chamath Palihapitiya. Reforce founder and CEO Brian Balfour shares:
“Growth (the kind found on an org chart) began at Facebook under the direction of Chamath Palihapitiya. In 2007, he joined the early team in a nebulous role that fell somewhere between Product, Marketing, and Operations. According to his retelling of the story on Recode Decode, after struggling to accomplish anything meaningful in his first year on the job, he was on the verge of being fired.Sheryl Sandberg joined soon after him, and in a hail mary move he pitched her the game-changing idea that led to the creation of the first-ever growth team. This idea not only saved his job, but earned him the lion’s share of the credit for Facebook’s unprecedented growth.At the time, Sheryl and Mark asked him, “What do you call this thing where you help change the product, do some SEO and SEM, and algorithmically do this or that?”His response: “I don’t know, I just call that, like, Growth, you know, we’re going to try to grow. I’ll be the head of growing stuff."And just like that, Growth became a thing.”
Rather than focus on a particular product or feature, the growth team at Facebook focused on moving the needle, and figuring out which features to work on. These days, Meta employs hundreds if not thousands of growth engineers.
2. What do Growth Engineers work on?
Before we jump into concrete examples, let’s identify three primary focus areas that a growth engineer’s work usually involves.
- Business-facing work – improving the business directly
- Empowerment work – enabling other teams to improve the business
- Platform work – improving the velocity of the above activities
Let’s go through all three:
Business-facing work
This is the bread and butter of growth engineering, and follows a common pattern:
- Implement an idea. Try something big or small to try and move a key business metric, which differs by team but is typically related to conversion rate or retention.
- Quantify impact. Usually via A/B testing.
- Analyze impact. Await results, analyze impact, ship or roll back – then go back to the first step.
Experiments can lead to sweeping or barely noticeable changes. A famous “I can’t believe they needed to test this” was when Google figured out which shade of blue generates the most clicks. At MasterClass, we tested things across the spectrum:
- Small: should we show the price right on the homepage, was that a winner? Yes, but we framed it in monthly terms of $15/month, not $180/year.
- Medium: when browsing a course page, should we include related courses, or more details about the course itself? Was it a winner? After lengthy experimentation, it was hard to tell: both are valuable and we needed to strike the right balance.
- Large: when a potential customer is interested, do we take them straight to checkout, or encourage them to learn more? Counterintuitively, adding steps boosted conversion!
Empowerment
One of the best ways an engineer can move a target metric is by removing themselves as a bottleneck, so colleagues from marketing can iterate and optimize freely. To this end, growth engineers can either build internal tools or integrate self-serve MarTech (Marketing Technology) vendors.
With the right tool, there’s a lot that marketers can do without engineering’s involvement:
- Build and iterate on landing pages (Unbounce, Instapage, etc)
- Draft and send email, SMS and Push Notifications (Iterable, Braze, Customer.io, etc)
- Connect new advertising partners (Google Tag Manager, Segment, etc)
We go more into detail about benefits and applications in the MarTech section of Tech Stack, below.
Platform work
As a business scales, dedicated platform teams help improve stability and velocity for the teams they support. Within growth, this often includes initiatives like:
- Experiment Platform. Many parts of running an experiment can be standardized, from filtering the audience, to bucketing users properly, to observing statistical methodology. Historically, companies built reusable Experiment Platforms in-house, but more recently, vendors such as Eppo and Statsig have grown in popularity with fancy statistical methodologies like “Controlled Using Pre-Experiment Data” (CUPED) that give more signal with less data.
- Reusable components. Companies with standard front-end components for things like headlines, buttons, and images, dramatically reduce the time required to spin up a new page. No more "did you want 5 or 6 pixels here" with a designer; instead growth engineers rely on tools like Storybook to standardize and share reusable React components.
- Monitoring. Growth engineering benefits greatly from leveraging monitoring to compensate for reduced code coverage. High-quality business metric monitoring tools can detect bugs before they cause damage.
When I worked at MasterClass, having monitoring at the ad layer prevented at least one six-figure incident. One Friday, a marketer accidentally broadened the audience for a particular ad from US-only, to worldwide. In response, the Facebook Ad algorithm went on a spending spree, bringing in plenty of visitors from places like Brazil and India, whom we knew from past experience were unlikely to purchase the product. Fortunately, our monitoring noticed the low-performing campaign within minutes, and an alert was sent to the growth engineer on-call, who immediately reached out to the marketer and confirmed the change was unintentional, and then shut down the campaign.
Without this monitoring, a subtle targeting error like this could have gone unnoticed all weekend and would have eaten up $100,000+ of marketing budget. This episode shows that platform investment can benefit everyone; and since growth needs them most, it’s often the growth platform engineering team which implements them.
As the day-to-day work of a Growth Engineer shows, A/B tests are a critical tool to both measure success and learn. It’s a numbers game: the more A/B tests a team can run in a given quarter, the more of them will end up winners, making the team successful. It’s no wonder, then, that Growth Engineering will pull out all the stops to improve velocity.
3. Why Growth Engineers move faster than Product Engineers
On the surface, growth engineering teams look like product engineering ones; writing code, shipping pull requests, monitoring on-call, etc. So how do they move so much faster? The big reason lies in philosophy and focus, not technology. To quote Elena Verna, head of growth at Dropbox:
“Product Engineering teams ship to build; Growth Engineering teams ship to learn.”
Real-world case: price changes at Masterclass
A few years ago at MasterClass, the growth team wanted to see if changing our pricing model to multiple tiers would improve revenue.
Inspired in part by multiple pricing tiers for competitors such as Netflix (above), Disney Plus, and Hulu.
The “multiple pricing tier” proposal for MasterClass.
From a software engineering perspective, this was a highly complex project because:
- Backend engineering work: the backend did not yet support multiple pricing options, requiring a decent amount of engineering, and rigorous testing to make sure existing customers weren’t affected.
- Client app changes: on the device side, multiple platforms (iOS, iPad, Android, Roku, Apple TV, etc) would each need to be updated, including each relevant app store.
The software engineering team estimated that becoming a “multi-pricing-tier” company would take months across numerous engineering teams, and engineering leadership was unwilling to greenlight that significant investment.
We in growth engineering took this as a challenge. As usual, our goal was not just to add the new pricing model, but to learn how much money it might bring in. The approach we ended up proposing was a Fake Door test, which involves offering a not-yet-available option to customers to gauge interest level. This was risky, as taking a customer who’s ready to pay and telling them to join some kind of waiting list is a colossal waste, and risks making them feel like the target of a “bait and switch” trick.
We found a way. The key insight was that people are only offended about a “bait and switch”, if the “switch” is worse than the “bait.” Telling customers they would pay $100 and then switching to $150 would cause a riot, but starting at $150 and then saying “just kidding, it’s only $100” is a pleasant surprise.
The good kind of surprise.
So long as every test “pricing tier” is less appealing – higher prices, fewer features – than the current offering, we could “upgrade” customers after their initial selection. A customer choosing the cheapest tier gets extra features at no extra cost, while a customer choosing a more expensive tier is offered a discount.
We created three new tiers, at different prices. The new “premium” tier would describe the existing, original offering. Regardless of what potential customers selected, they got this “original offering,” during the experiment.
The best thing about this was that no backend changes were required. There were no real, new, back-end pricing plans; everybody ended up purchasing the same version of MasterClass for the same price, with the same features. The entirety of the engineering work was on building a new pricing page, and the “congratulations, you’ve been upgraded” popup. This took just a few days.
Within a couple of weeks, we had enough data to be confident the financial upside of moving to a multi-pricing-tier model would be significant. With this, we’re able to convince the rest of engineering’s leadership to invest in building the feature properly. In the end, launching multiple pricing tiers turned out to be one of the biggest revenue wins of the year.
Building a skyscraper vs building a tent
The MasterClass example demonstrates the spirit of growth engineering; focusing on building to learn, instead of building to last. Consider building skyscrapers versus tents.
Building a tent optimizes for speed of set-up and tear-down over longevity. You don’t think of a tent as one that is shoddy or low-quality compared to skyscrapers: it’s not even the same category of buildings! Growth engineers maximize use of lightweight materials. To stick with the tents vs skyscraper metaphor: we prioritize lightweight fabric materials over steel and concrete whenever possible. We only resort to traditional building materials when there’s no other choice, or when a direction is confirmed as correct. Quality is important – after all, a tent must keep out rain and mosquitoes. However, the speed-vs-durability tradeoff decision results in very different approaches and outcomes.
4. Tech stack
At first glance, growth and product engineers use the same tooling, and contribute to the same codebases. But growth engineering tends to be high-velocity, experiment-heavy, and with limited test coverage. This means that certain “nice to have” tools for product engineering are mission-critical for growth engineers.
Read more https://connect-test.layer3.press/articles/ea02c1a1-7cfa-42b4-8722-0165abcae8bb
-
 @ 04c915da:3dfbecc9
2025-03-26 20:54:33
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 04c915da:3dfbecc9
2025-03-10 23:31:30
@ 04c915da:3dfbecc9
2025-03-10 23:31:30Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Usually stolen bitcoin for the reserve creates a perverse incentive. If governments see a bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 04c915da:3dfbecc9
2025-03-07 00:26:37
@ 04c915da:3dfbecc9
2025-03-07 00:26:37There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ 04c915da:3dfbecc9
2025-03-04 17:00:18
@ 04c915da:3dfbecc9
2025-03-04 17:00:18This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ 04c915da:3dfbecc9
2025-02-25 03:55:08
@ 04c915da:3dfbecc9
2025-02-25 03:55:08Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 6e0ea5d6:0327f353
2025-02-21 18:15:52
@ 6e0ea5d6:0327f353
2025-02-21 18:15:52"Malcolm Forbes recounts that a lady, wearing a faded cotton dress, and her husband, dressed in an old handmade suit, stepped off a train in Boston, USA, and timidly made their way to the office of the president of Harvard University. They had come from Palo Alto, California, and had not scheduled an appointment. The secretary, at a glance, thought that those two, looking like country bumpkins, had no business at Harvard.
— We want to speak with the president — the man said in a low voice.
— He will be busy all day — the secretary replied curtly.
— We will wait.
The secretary ignored them for hours, hoping the couple would finally give up and leave. But they stayed there, and the secretary, somewhat frustrated, decided to bother the president, although she hated doing that.
— If you speak with them for just a few minutes, maybe they will decide to go away — she said.
The president sighed in irritation but agreed. Someone of his importance did not have time to meet people like that, but he hated faded dresses and tattered suits in his office. With a stern face, he went to the couple.
— We had a son who studied at Harvard for a year — the woman said. — He loved Harvard and was very happy here, but a year ago he died in an accident, and we would like to erect a monument in his honor somewhere on campus.— My lady — said the president rudely —, we cannot erect a statue for every person who studied at Harvard and died; if we did, this place would look like a cemetery.
— Oh, no — the lady quickly replied. — We do not want to erect a statue. We would like to donate a building to Harvard.
The president looked at the woman's faded dress and her husband's old suit and exclaimed:
— A building! Do you have even the faintest idea of how much a building costs? We have more than seven and a half million dollars' worth of buildings here at Harvard.
The lady was silent for a moment, then said to her husband:
— If that’s all it costs to found a university, why don’t we have our own?
The husband agreed.
The couple, Leland Stanford, stood up and left, leaving the president confused. Traveling back to Palo Alto, California, they established there Stanford University, the second-largest in the world, in honor of their son, a former Harvard student."
Text extracted from: "Mileumlivros - Stories that Teach Values."
Thank you for reading, my friend! If this message helped you in any way, consider leaving your glass “🥃” as a token of appreciation.
A toast to our family!
-
 @ 0fa80bd3:ea7325de
2025-02-14 23:24:37
@ 0fa80bd3:ea7325de
2025-02-14 23:24:37intro
The Russian state made me a Bitcoiner. In 1991, it devalued my grandmother's hard-earned savings. She worked tirelessly in the kitchen of a dining car on the Moscow–Warsaw route. Everything she had saved for my sister and me to attend university vanished overnight. This story is similar to what many experienced, including Wences Casares. The pain and injustice of that time became my first lessons about the fragility of systems and the value of genuine, incorruptible assets, forever changing my perception of money and my trust in government promises.
In 2014, I was living in Moscow, running a trading business, and frequently traveling to China. One day, I learned about the Cypriot banking crisis and the possibility of moving money through some strange thing called Bitcoin. At the time, I didn’t give it much thought. Returning to the idea six months later, as a business-oriented geek, I eagerly began studying the topic and soon dove into it seriously.
I spent half a year reading articles on a local online journal, BitNovosti, actively participating in discussions, and eventually joined the editorial team as a translator. That’s how I learned about whitepapers, decentralization, mining, cryptographic keys, and colored coins. About Satoshi Nakamoto, Silk Road, Mt. Gox, and BitcoinTalk. Over time, I befriended the journal’s owner and, leveraging my management experience, later became an editor. I was drawn to the crypto-anarchist stance and commitment to decentralization principles. We wrote about the economic, historical, and social preconditions for Bitcoin’s emergence, and it was during this time that I fully embraced the idea.
It got to the point where I sold my apartment and, during the market's downturn, bought 50 bitcoins, just after the peak price of $1,200 per coin. That marked the beginning of my first crypto winter. As an editor, I organized workflows, managed translators, developed a YouTube channel, and attended conferences in Russia and Ukraine. That’s how I learned about Wences Casares and even wrote a piece about him. I also met Mikhail Chobanyan (Ukrainian exchange Kuna), Alexander Ivanov (Waves project), Konstantin Lomashuk (Lido project), and, of course, Vitalik Buterin. It was a time of complete immersion, 24/7, and boundless hope.
After moving to the United States, I expected the industry to grow rapidly, attended events, but the introduction of BitLicense froze the industry for eight years. By 2017, it became clear that the industry was shifting toward gambling and creating tokens for the sake of tokens. I dismissed this idea as unsustainable. Then came a new crypto spring with the hype around beautiful NFTs – CryptoPunks and apes.
I made another attempt – we worked on a series called Digital Nomad Country Club, aimed at creating a global project. The proceeds from selling images were intended to fund the development of business tools for people worldwide. However, internal disagreements within the team prevented us from completing the project.
With Trump’s arrival in 2025, hope was reignited. I decided that it was time to create a project that society desperately needed. As someone passionate about history, I understood that destroying what exists was not the solution, but leaving everything as it was also felt unacceptable. You can’t destroy the system, as the fiery crypto-anarchist voices claimed.
With an analytical mindset (IQ 130) and a deep understanding of the freest societies, I realized what was missing—not only in Russia or the United States but globally—a Bitcoin-native system for tracking debts and financial interactions. This could return control of money to ordinary people and create horizontal connections parallel to state systems. My goal was to create, if not a Bitcoin killer app, then at least to lay its foundation.
At the inauguration event in New York, I rediscovered the Nostr project. I realized it was not only technologically simple and already quite popular but also perfectly aligned with my vision. For the past month and a half, using insights and experience gained since 2014, I’ve been working full-time on this project.
-
 @ daa41bed:88f54153
2025-02-09 16:50:04
@ daa41bed:88f54153
2025-02-09 16:50:04There has been a good bit of discussion on Nostr over the past few days about the merits of zaps as a method of engaging with notes, so after writing a rather lengthy article on the pros of a strategic Bitcoin reserve, I wanted to take some time to chime in on the much more fun topic of digital engagement.
Let's begin by defining a couple of things:
Nostr is a decentralized, censorship-resistance protocol whose current biggest use case is social media (think Twitter/X). Instead of relying on company servers, it relies on relays that anyone can spin up and own their own content. Its use cases are much bigger, though, and this article is hosted on my own relay, using my own Nostr relay as an example.
Zap is a tip or donation denominated in sats (small units of Bitcoin) sent from one user to another. This is generally done directly over the Lightning Network but is increasingly using Cashu tokens. For the sake of this discussion, how you transmit/receive zaps will be irrelevant, so don't worry if you don't know what Lightning or Cashu are.
If we look at how users engage with posts and follows/followers on platforms like Twitter, Facebook, etc., it becomes evident that traditional social media thrives on engagement farming. The more outrageous a post, the more likely it will get a reaction. We see a version of this on more visual social platforms like YouTube and TikTok that use carefully crafted thumbnail images to grab the user's attention to click the video. If you'd like to dive deep into the psychology and science behind social media engagement, let me know, and I'd be happy to follow up with another article.
In this user engagement model, a user is given the option to comment or like the original post, or share it among their followers to increase its signal. They receive no value from engaging with the content aside from the dopamine hit of the original experience or having their comment liked back by whatever influencer they provide value to. Ad revenue flows to the content creator. Clout flows to the content creator. Sales revenue from merch and content placement flows to the content creator. We call this a linear economy -- the idea that resources get created, used up, then thrown away. Users create content and farm as much engagement as possible, then the content is forgotten within a few hours as they move on to the next piece of content to be farmed.
What if there were a simple way to give value back to those who engage with your content? By implementing some value-for-value model -- a circular economy. Enter zaps.

Unlike traditional social media platforms, Nostr does not actively use algorithms to determine what content is popular, nor does it push content created for active user engagement to the top of a user's timeline. Yes, there are "trending" and "most zapped" timelines that users can choose to use as their default, but these use relatively straightforward engagement metrics to rank posts for these timelines.
That is not to say that we may not see clients actively seeking to refine timeline algorithms for specific metrics. Still, the beauty of having an open protocol with media that is controlled solely by its users is that users who begin to see their timeline gamed towards specific algorithms can choose to move to another client, and for those who are more tech-savvy, they can opt to run their own relays or create their own clients with personalized algorithms and web of trust scoring systems.
Zaps enable the means to create a new type of social media economy in which creators can earn for creating content and users can earn by actively engaging with it. Like and reposting content is relatively frictionless and costs nothing but a simple button tap. Zaps provide active engagement because they signal to your followers and those of the content creator that this post has genuine value, quite literally in the form of money—sats.

I have seen some comments on Nostr claiming that removing likes and reactions is for wealthy people who can afford to send zaps and that the majority of people in the US and around the world do not have the time or money to zap because they have better things to spend their money like feeding their families and paying their bills. While at face value, these may seem like valid arguments, they, unfortunately, represent the brainwashed, defeatist attitude that our current economic (and, by extension, social media) systems aim to instill in all of us to continue extracting value from our lives.
Imagine now, if those people dedicating their own time (time = money) to mine pity points on social media would instead spend that time with genuine value creation by posting content that is meaningful to cultural discussions. Imagine if, instead of complaining that their posts get no zaps and going on a tirade about how much of a victim they are, they would empower themselves to take control of their content and give value back to the world; where would that leave us? How much value could be created on a nascent platform such as Nostr, and how quickly could it overtake other platforms?
Other users argue about user experience and that additional friction (i.e., zaps) leads to lower engagement, as proven by decades of studies on user interaction. While the added friction may turn some users away, does that necessarily provide less value? I argue quite the opposite. You haven't made a few sats from zaps with your content? Can't afford to send some sats to a wallet for zapping? How about using the most excellent available resource and spending 10 seconds of your time to leave a comment? Likes and reactions are valueless transactions. Social media's real value derives from providing monetary compensation and actively engaging in a conversation with posts you find interesting or thought-provoking. Remember when humans thrived on conversation and discussion for entertainment instead of simply being an onlooker of someone else's life?
If you've made it this far, my only request is this: try only zapping and commenting as a method of engagement for two weeks. Sure, you may end up liking a post here and there, but be more mindful of how you interact with the world and break yourself from blind instinct. You'll thank me later.

-
 @ e3ba5e1a:5e433365
2025-02-05 17:47:16
@ e3ba5e1a:5e433365
2025-02-05 17:47:16I got into a friendly discussion on X regarding health insurance. The specific question was how to deal with health insurance companies (presumably unfairly) denying claims? My answer, as usual: get government out of it!
The US healthcare system is essentially the worst of both worlds:
- Unlike full single payer, individuals incur high costs
- Unlike a true free market, regulation causes increases in costs and decreases competition among insurers
I'm firmly on the side of moving towards the free market. (And I say that as someone living under a single payer system now.) Here's what I would do:
- Get rid of tax incentives that make health insurance tied to your employer, giving individuals back proper freedom of choice.
- Reduce regulations significantly.
-
In the short term, some people will still get rejected claims and other obnoxious behavior from insurance companies. We address that in two ways:
- Due to reduced regulations, new insurance companies will be able to enter the market offering more reliable coverage and better rates, and people will flock to them because they have the freedom to make their own choices.
- Sue the asses off of companies that reject claims unfairly. And ideally, as one of the few legitimate roles of government in all this, institute new laws that limit the ability of fine print to allow insurers to escape their responsibilities. (I'm hesitant that the latter will happen due to the incestuous relationship between Congress/regulators and insurers, but I can hope.)
Will this magically fix everything overnight like politicians normally promise? No. But it will allow the market to return to a healthy state. And I don't think it will take long (order of magnitude: 5-10 years) for it to come together, but that's just speculation.
And since there's a high correlation between those who believe government can fix problems by taking more control and demanding that only credentialed experts weigh in on a topic (both points I strongly disagree with BTW): I'm a trained actuary and worked in the insurance industry, and have directly seen how government regulation reduces competition, raises prices, and harms consumers.
And my final point: I don't think any prior art would be a good comparison for deregulation in the US, it's such a different market than any other country in the world for so many reasons that lessons wouldn't really translate. Nonetheless, I asked Grok for some empirical data on this, and at best the results of deregulation could be called "mixed," but likely more accurately "uncertain, confused, and subject to whatever interpretation anyone wants to apply."
https://x.com/i/grok/share/Zc8yOdrN8lS275hXJ92uwq98M
-
 @ 9e69e420:d12360c2
2025-02-01 11:16:04
@ 9e69e420:d12360c2
2025-02-01 11:16:04Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.

CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language.
One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse.
-
 @ 0fa80bd3:ea7325de
2025-01-29 05:55:02
@ 0fa80bd3:ea7325de
2025-01-29 05:55:02The land that belongs to the indigenous peoples of Russia has been seized by a gang of killers who have unleashed a war of extermination. They wipe out anyone who refuses to conform to their rules. Those who disagree and stay behind are tortured and killed in prisons and labor camps. Those who flee lose their homeland, dissolve into foreign cultures, and fade away. And those who stand up to protect their people are attacked by the misled and deceived. The deceived die for the unchecked greed of a single dictator—thousands from both sides, people who just wanted to live, raise their kids, and build a future.
Now, they are forced to make an impossible choice: abandon their homeland or die. Some perish on the battlefield, others lose themselves in exile, stripped of their identity, scattered in a world that isn’t theirs.
There’s been endless debate about how to fix this, how to clear the field of the weeds that choke out every new sprout, every attempt at change. But the real problem? We can’t play by their rules. We can’t speak their language or use their weapons. We stand for humanity, and no matter how righteous our cause, we will not multiply suffering. Victory doesn’t come from matching the enemy—it comes from staying ahead, from using tools they haven’t mastered yet. That’s how wars are won.
Our only resource is the will of the people to rewrite the order of things. Historian Timothy Snyder once said that a nation cannot exist without a city. A city is where the most active part of a nation thrives. But the cities are occupied. The streets are watched. Gatherings are impossible. They control the money. They control the mail. They control the media. And any dissent is crushed before it can take root.
So I started asking myself: How do we stop this fragmentation? How do we create a space where people can rebuild their connections when they’re ready? How do we build a self-sustaining network, where everyone contributes and benefits proportionally, while keeping their freedom to leave intact? And more importantly—how do we make it spread, even in occupied territory?
In 2009, something historic happened: the internet got its own money. Thanks to Satoshi Nakamoto, the world took a massive leap forward. Bitcoin and decentralized ledgers shattered the idea that money must be controlled by the state. Now, to move or store value, all you need is an address and a key. A tiny string of text, easy to carry, impossible to seize.
That was the year money broke free. The state lost its grip. Its biggest weapon—physical currency—became irrelevant. Money became purely digital.
The internet was already a sanctuary for information, a place where people could connect and organize. But with Bitcoin, it evolved. Now, value itself could flow freely, beyond the reach of authorities.
Think about it: when seedlings are grown in controlled environments before being planted outside, they get stronger, survive longer, and bear fruit faster. That’s how we handle crops in harsh climates—nurture them until they’re ready for the wild.
Now, picture the internet as that controlled environment for ideas. Bitcoin? It’s the fertile soil that lets them grow. A testing ground for new models of interaction, where concepts can take root before they move into the real world. If nation-states are a battlefield, locked in a brutal war for territory, the internet is boundless. It can absorb any number of ideas, any number of people, and it doesn’t run out of space.
But for this ecosystem to thrive, people need safe ways to communicate, to share ideas, to build something real—without surveillance, without censorship, without the constant fear of being erased.
This is where Nostr comes in.
Nostr—"Notes and Other Stuff Transmitted by Relays"—is more than just a messaging protocol. It’s a new kind of city. One that no dictator can seize, no corporation can own, no government can shut down.
It’s built on decentralization, encryption, and individual control. Messages don’t pass through central servers—they are relayed through independent nodes, and users choose which ones to trust. There’s no master switch to shut it all down. Every person owns their identity, their data, their connections. And no one—no state, no tech giant, no algorithm—can silence them.
In a world where cities fall and governments fail, Nostr is a city that cannot be occupied. A place for ideas, for networks, for freedom. A city that grows stronger the more people build within it.
-
 @ 6be5cc06:5259daf0
2025-01-21 20:58:37
@ 6be5cc06:5259daf0
2025-01-21 20:58:37A seguir, veja como instalar e configurar o Privoxy no Pop!_OS.
1. Instalar o Tor e o Privoxy
Abra o terminal e execute:
bash sudo apt update sudo apt install tor privoxyExplicação:
- Tor: Roteia o tráfego pela rede Tor.
- Privoxy: Proxy avançado que intermedia a conexão entre aplicativos e o Tor.
2. Configurar o Privoxy
Abra o arquivo de configuração do Privoxy:
bash sudo nano /etc/privoxy/configNavegue até a última linha (atalho:
Ctrl+/depoisCtrl+Vpara navegar diretamente até a última linha) e insira:bash forward-socks5 / 127.0.0.1:9050 .Isso faz com que o Privoxy envie todo o tráfego para o Tor através da porta 9050.
Salve (
CTRL+OeEnter) e feche (CTRL+X) o arquivo.
3. Iniciar o Tor e o Privoxy
Agora, inicie e habilite os serviços:
bash sudo systemctl start tor sudo systemctl start privoxy sudo systemctl enable tor sudo systemctl enable privoxyExplicação:
- start: Inicia os serviços.
- enable: Faz com que iniciem automaticamente ao ligar o PC.
4. Configurar o Navegador Firefox
Para usar a rede Tor com o Firefox:
- Abra o Firefox.
- Acesse Configurações → Configurar conexão.
- Selecione Configuração manual de proxy.
- Configure assim:
- Proxy HTTP:
127.0.0.1 - Porta:
8118(porta padrão do Privoxy) - Domínio SOCKS (v5):
127.0.0.1 - Porta:
9050
- Proxy HTTP:
- Marque a opção "Usar este proxy também em HTTPS".
- Clique em OK.
5. Verificar a Conexão com o Tor
Abra o navegador e acesse:
text https://check.torproject.org/Se aparecer a mensagem "Congratulations. This browser is configured to use Tor.", a configuração está correta.
Dicas Extras
- Privoxy pode ser ajustado para bloquear anúncios e rastreadores.
- Outros aplicativos também podem ser configurados para usar o Privoxy.
-
 @ 9e69e420:d12360c2
2025-01-21 19:31:48
@ 9e69e420:d12360c2
2025-01-21 19:31:48Oregano oil is a potent natural compound that offers numerous scientifically-supported health benefits.
Active Compounds
The oil's therapeutic properties stem from its key bioactive components: - Carvacrol and thymol (primary active compounds) - Polyphenols and other antioxidant
Antimicrobial Properties
Bacterial Protection The oil demonstrates powerful antibacterial effects, even against antibiotic-resistant strains like MRSA and other harmful bacteria. Studies show it effectively inactivates various pathogenic bacteria without developing resistance.
Antifungal Effects It effectively combats fungal infections, particularly Candida-related conditions like oral thrush, athlete's foot, and nail infections.
Digestive Health Benefits
Oregano oil supports digestive wellness by: - Promoting gastric juice secretion and enzyme production - Helping treat Small Intestinal Bacterial Overgrowth (SIBO) - Managing digestive discomfort, bloating, and IBS symptoms
Anti-inflammatory and Antioxidant Effects
The oil provides significant protective benefits through: - Powerful antioxidant activity that fights free radicals - Reduction of inflammatory markers in the body - Protection against oxidative stress-related conditions
Respiratory Support
It aids respiratory health by: - Loosening mucus and phlegm - Suppressing coughs and throat irritation - Supporting overall respiratory tract function
Additional Benefits
Skin Health - Improves conditions like psoriasis, acne, and eczema - Supports wound healing through antibacterial action - Provides anti-aging benefits through antioxidant properties
Cardiovascular Health Studies show oregano oil may help: - Reduce LDL (bad) cholesterol levels - Support overall heart health
Pain Management The oil demonstrates effectiveness in: - Reducing inflammation-related pain - Managing muscle discomfort - Providing topical pain relief
Safety Note
While oregano oil is generally safe, it's highly concentrated and should be properly diluted before use Consult a healthcare provider before starting supplementation, especially if taking other medications.
-
 @ 6be5cc06:5259daf0
2025-01-21 01:51:46
@ 6be5cc06:5259daf0
2025-01-21 01:51:46Bitcoin: Um sistema de dinheiro eletrônico direto entre pessoas.
Satoshi Nakamoto
satoshin@gmx.com
www.bitcoin.org
Resumo
O Bitcoin é uma forma de dinheiro digital que permite pagamentos diretos entre pessoas, sem a necessidade de um banco ou instituição financeira. Ele resolve um problema chamado gasto duplo, que ocorre quando alguém tenta gastar o mesmo dinheiro duas vezes. Para evitar isso, o Bitcoin usa uma rede descentralizada onde todos trabalham juntos para verificar e registrar as transações.
As transações são registradas em um livro público chamado blockchain, protegido por uma técnica chamada Prova de Trabalho. Essa técnica cria uma cadeia de registros que não pode ser alterada sem refazer todo o trabalho já feito. Essa cadeia é mantida pelos computadores que participam da rede, e a mais longa é considerada a verdadeira.
Enquanto a maior parte do poder computacional da rede for controlada por participantes honestos, o sistema continuará funcionando de forma segura. A rede é flexível, permitindo que qualquer pessoa entre ou saia a qualquer momento, sempre confiando na cadeia mais longa como prova do que aconteceu.
1. Introdução
Hoje, quase todos os pagamentos feitos pela internet dependem de bancos ou empresas como processadores de pagamento (cartões de crédito, por exemplo) para funcionar. Embora esse sistema seja útil, ele tem problemas importantes porque é baseado em confiança.
Primeiro, essas empresas podem reverter pagamentos, o que é útil em caso de erros, mas cria custos e incertezas. Isso faz com que pequenas transações, como pagar centavos por um serviço, se tornem inviáveis. Além disso, os comerciantes são obrigados a desconfiar dos clientes, pedindo informações extras e aceitando fraudes como algo inevitável.
Esses problemas não existem no dinheiro físico, como o papel-moeda, onde o pagamento é final e direto entre as partes. No entanto, não temos como enviar dinheiro físico pela internet sem depender de um intermediário confiável.
O que precisamos é de um sistema de pagamento eletrônico baseado em provas matemáticas, não em confiança. Esse sistema permitiria que qualquer pessoa enviasse dinheiro diretamente para outra, sem depender de bancos ou processadores de pagamento. Além disso, as transações seriam irreversíveis, protegendo vendedores contra fraudes, mas mantendo a possibilidade de soluções para disputas legítimas.
Neste documento, apresentamos o Bitcoin, que resolve o problema do gasto duplo usando uma rede descentralizada. Essa rede cria um registro público e protegido por cálculos matemáticos, que garante a ordem das transações. Enquanto a maior parte da rede for controlada por pessoas honestas, o sistema será seguro contra ataques.
2. Transações
Para entender como funciona o Bitcoin, é importante saber como as transações são realizadas. Imagine que você quer transferir uma "moeda digital" para outra pessoa. No sistema do Bitcoin, essa "moeda" é representada por uma sequência de registros que mostram quem é o atual dono. Para transferi-la, você adiciona um novo registro comprovando que agora ela pertence ao próximo dono. Esse registro é protegido por um tipo especial de assinatura digital.
O que é uma assinatura digital?
Uma assinatura digital é como uma senha secreta, mas muito mais segura. No Bitcoin, cada usuário tem duas chaves: uma "chave privada", que é secreta e serve para criar a assinatura, e uma "chave pública", que pode ser compartilhada com todos e é usada para verificar se a assinatura é válida. Quando você transfere uma moeda, usa sua chave privada para assinar a transação, provando que você é o dono. A próxima pessoa pode usar sua chave pública para confirmar isso.
Como funciona na prática?
Cada "moeda" no Bitcoin é, na verdade, uma cadeia de assinaturas digitais. Vamos imaginar o seguinte cenário:
- A moeda está com o Dono 0 (você). Para transferi-la ao Dono 1, você assina digitalmente a transação com sua chave privada. Essa assinatura inclui o código da transação anterior (chamado de "hash") e a chave pública do Dono 1.
- Quando o Dono 1 quiser transferir a moeda ao Dono 2, ele assinará a transação seguinte com sua própria chave privada, incluindo também o hash da transação anterior e a chave pública do Dono 2.
- Esse processo continua, formando uma "cadeia" de transações. Qualquer pessoa pode verificar essa cadeia para confirmar quem é o atual dono da moeda.
Resolvendo o problema do gasto duplo
Um grande desafio com moedas digitais é o "gasto duplo", que é quando uma mesma moeda é usada em mais de uma transação. Para evitar isso, muitos sistemas antigos dependiam de uma entidade central confiável, como uma casa da moeda, que verificava todas as transações. No entanto, isso criava um ponto único de falha e centralizava o controle do dinheiro.
O Bitcoin resolve esse problema de forma inovadora: ele usa uma rede descentralizada onde todos os participantes (os "nós") têm acesso a um registro completo de todas as transações. Cada nó verifica se as transações são válidas e se a moeda não foi gasta duas vezes. Quando a maioria dos nós concorda com a validade de uma transação, ela é registrada permanentemente na blockchain.
Por que isso é importante?
Essa solução elimina a necessidade de confiar em uma única entidade para gerenciar o dinheiro, permitindo que qualquer pessoa no mundo use o Bitcoin sem precisar de permissão de terceiros. Além disso, ela garante que o sistema seja seguro e resistente a fraudes.
3. Servidor Timestamp
Para assegurar que as transações sejam realizadas de forma segura e transparente, o sistema Bitcoin utiliza algo chamado de "servidor de registro de tempo" (timestamp). Esse servidor funciona como um registro público que organiza as transações em uma ordem específica.
Ele faz isso agrupando várias transações em blocos e criando um código único chamado "hash". Esse hash é como uma impressão digital que representa todo o conteúdo do bloco. O hash de cada bloco é amplamente divulgado, como se fosse publicado em um jornal ou em um fórum público.
Esse processo garante que cada bloco de transações tenha um registro de quando foi criado e que ele existia naquele momento. Além disso, cada novo bloco criado contém o hash do bloco anterior, formando uma cadeia contínua de blocos conectados — conhecida como blockchain.
Com isso, se alguém tentar alterar qualquer informação em um bloco anterior, o hash desse bloco mudará e não corresponderá ao hash armazenado no bloco seguinte. Essa característica torna a cadeia muito segura, pois qualquer tentativa de fraude seria imediatamente detectada.
O sistema de timestamps é essencial para provar a ordem cronológica das transações e garantir que cada uma delas seja única e autêntica. Dessa forma, ele reforça a segurança e a confiança na rede Bitcoin.
4. Prova-de-Trabalho
Para implementar o registro de tempo distribuído no sistema Bitcoin, utilizamos um mecanismo chamado prova-de-trabalho. Esse sistema é semelhante ao Hashcash, desenvolvido por Adam Back, e baseia-se na criação de um código único, o "hash", por meio de um processo computacionalmente exigente.
A prova-de-trabalho envolve encontrar um valor especial que, quando processado junto com as informações do bloco, gere um hash que comece com uma quantidade específica de zeros. Esse valor especial é chamado de "nonce". Encontrar o nonce correto exige um esforço significativo do computador, porque envolve tentativas repetidas até que a condição seja satisfeita.
Esse processo é importante porque torna extremamente difícil alterar qualquer informação registrada em um bloco. Se alguém tentar mudar algo em um bloco, seria necessário refazer o trabalho de computação não apenas para aquele bloco, mas também para todos os blocos que vêm depois dele. Isso garante a segurança e a imutabilidade da blockchain.
A prova-de-trabalho também resolve o problema de decidir qual cadeia de blocos é a válida quando há múltiplas cadeias competindo. A decisão é feita pela cadeia mais longa, pois ela representa o maior esforço computacional já realizado. Isso impede que qualquer indivíduo ou grupo controle a rede, desde que a maioria do poder de processamento seja mantida por participantes honestos.
Para garantir que o sistema permaneça eficiente e equilibrado, a dificuldade da prova-de-trabalho é ajustada automaticamente ao longo do tempo. Se novos blocos estiverem sendo gerados rapidamente, a dificuldade aumenta; se estiverem sendo gerados muito lentamente, a dificuldade diminui. Esse ajuste assegura que novos blocos sejam criados aproximadamente a cada 10 minutos, mantendo o sistema estável e funcional.
5. Rede
A rede Bitcoin é o coração do sistema e funciona de maneira distribuída, conectando vários participantes (ou nós) para garantir o registro e a validação das transações. Os passos para operar essa rede são:
-
Transmissão de Transações: Quando alguém realiza uma nova transação, ela é enviada para todos os nós da rede. Isso é feito para garantir que todos estejam cientes da operação e possam validá-la.
-
Coleta de Transações em Blocos: Cada nó agrupa as novas transações recebidas em um "bloco". Este bloco será preparado para ser adicionado à cadeia de blocos (a blockchain).
-
Prova-de-Trabalho: Os nós competem para resolver a prova-de-trabalho do bloco, utilizando poder computacional para encontrar um hash válido. Esse processo é como resolver um quebra-cabeça matemático difícil.
-
Envio do Bloco Resolvido: Quando um nó encontra a solução para o bloco (a prova-de-trabalho), ele compartilha esse bloco com todos os outros nós na rede.
-
Validação do Bloco: Cada nó verifica o bloco recebido para garantir que todas as transações nele contidas sejam válidas e que nenhuma moeda tenha sido gasta duas vezes. Apenas blocos válidos são aceitos.
-
Construção do Próximo Bloco: Os nós que aceitaram o bloco começam a trabalhar na criação do próximo bloco, utilizando o hash do bloco aceito como base (hash anterior). Isso mantém a continuidade da cadeia.
Resolução de Conflitos e Escolha da Cadeia Mais Longa
Os nós sempre priorizam a cadeia mais longa, pois ela representa o maior esforço computacional já realizado, garantindo maior segurança. Se dois blocos diferentes forem compartilhados simultaneamente, os nós trabalharão no primeiro bloco recebido, mas guardarão o outro como uma alternativa. Caso o segundo bloco eventualmente forme uma cadeia mais longa (ou seja, tenha mais blocos subsequentes), os nós mudarão para essa nova cadeia.
Tolerância a Falhas
A rede é robusta e pode lidar com mensagens que não chegam a todos os nós. Uma transação não precisa alcançar todos os nós de imediato; basta que chegue a um número suficiente deles para ser incluída em um bloco. Da mesma forma, se um nó não receber um bloco em tempo hábil, ele pode solicitá-lo ao perceber que está faltando quando o próximo bloco é recebido.
Esse mecanismo descentralizado permite que a rede Bitcoin funcione de maneira segura, confiável e resiliente, sem depender de uma autoridade central.
6. Incentivo
O incentivo é um dos pilares fundamentais que sustenta o funcionamento da rede Bitcoin, garantindo que os participantes (nós) continuem operando de forma honesta e contribuindo com recursos computacionais. Ele é estruturado em duas partes principais: a recompensa por mineração e as taxas de transação.
Recompensa por Mineração
Por convenção, o primeiro registro em cada bloco é uma transação especial que cria novas moedas e as atribui ao criador do bloco. Essa recompensa incentiva os mineradores a dedicarem poder computacional para apoiar a rede. Como não há uma autoridade central para emitir moedas, essa é a maneira pela qual novas moedas entram em circulação. Esse processo pode ser comparado ao trabalho de garimpeiros, que utilizam recursos para colocar mais ouro em circulação. No caso do Bitcoin, o "recurso" consiste no tempo de CPU e na energia elétrica consumida para resolver a prova-de-trabalho.
Taxas de Transação
Além da recompensa por mineração, os mineradores também podem ser incentivados pelas taxas de transação. Se uma transação utiliza menos valor de saída do que o valor de entrada, a diferença é tratada como uma taxa, que é adicionada à recompensa do bloco contendo essa transação. Com o passar do tempo e à medida que o número de moedas em circulação atinge o limite predeterminado, essas taxas de transação se tornam a principal fonte de incentivo, substituindo gradualmente a emissão de novas moedas. Isso permite que o sistema opere sem inflação, uma vez que o número total de moedas permanece fixo.
Incentivo à Honestidade
O design do incentivo também busca garantir que os participantes da rede mantenham um comportamento honesto. Para um atacante que consiga reunir mais poder computacional do que o restante da rede, ele enfrentaria duas escolhas:
- Usar esse poder para fraudar o sistema, como reverter transações e roubar pagamentos.
- Seguir as regras do sistema, criando novos blocos e recebendo recompensas legítimas.
A lógica econômica favorece a segunda opção, pois um comportamento desonesto prejudicaria a confiança no sistema, diminuindo o valor de todas as moedas, incluindo aquelas que o próprio atacante possui. Jogar dentro das regras não apenas maximiza o retorno financeiro, mas também preserva a validade e a integridade do sistema.
Esse mecanismo garante que os incentivos econômicos estejam alinhados com o objetivo de manter a rede segura, descentralizada e funcional ao longo do tempo.
7. Recuperação do Espaço em Disco
Depois que uma moeda passa a estar protegida por muitos blocos na cadeia, as informações sobre as transações antigas que a geraram podem ser descartadas para economizar espaço em disco. Para que isso seja possível sem comprometer a segurança, as transações são organizadas em uma estrutura chamada "árvore de Merkle". Essa árvore funciona como um resumo das transações: em vez de armazenar todas elas, guarda apenas um "hash raiz", que é como uma assinatura compacta que representa todo o grupo de transações.
Os blocos antigos podem, então, ser simplificados, removendo as partes desnecessárias dessa árvore. Apenas a raiz do hash precisa ser mantida no cabeçalho do bloco, garantindo que a integridade dos dados seja preservada, mesmo que detalhes específicos sejam descartados.
Para exemplificar: imagine que você tenha vários recibos de compra. Em vez de guardar todos os recibos, você cria um documento e lista apenas o valor total de cada um. Mesmo que os recibos originais sejam descartados, ainda é possível verificar a soma com base nos valores armazenados.
Além disso, o espaço ocupado pelos blocos em si é muito pequeno. Cada bloco sem transações ocupa apenas cerca de 80 bytes. Isso significa que, mesmo com blocos sendo gerados a cada 10 minutos, o crescimento anual em espaço necessário é insignificante: apenas 4,2 MB por ano. Com a capacidade de armazenamento dos computadores crescendo a cada ano, esse espaço continuará sendo trivial, garantindo que a rede possa operar de forma eficiente sem problemas de armazenamento, mesmo a longo prazo.
8. Verificação de Pagamento Simplificada
É possível confirmar pagamentos sem a necessidade de operar um nó completo da rede. Para isso, o usuário precisa apenas de uma cópia dos cabeçalhos dos blocos da cadeia mais longa (ou seja, a cadeia com maior esforço de trabalho acumulado). Ele pode verificar a validade de uma transação ao consultar os nós da rede até obter a confirmação de que tem a cadeia mais longa. Para isso, utiliza-se o ramo Merkle, que conecta a transação ao bloco em que ela foi registrada.
Entretanto, o método simplificado possui limitações: ele não pode confirmar uma transação isoladamente, mas sim assegurar que ela ocupa um lugar específico na cadeia mais longa. Dessa forma, se um nó da rede aprova a transação, os blocos subsequentes reforçam essa aceitação.
A verificação simplificada é confiável enquanto a maioria dos nós da rede for honesta. Contudo, ela se torna vulnerável caso a rede seja dominada por um invasor. Nesse cenário, um atacante poderia fabricar transações fraudulentas que enganariam o usuário temporariamente até que o invasor obtivesse controle completo da rede.
Uma estratégia para mitigar esse risco é configurar alertas nos softwares de nós completos. Esses alertas identificam blocos inválidos, sugerindo ao usuário baixar o bloco completo para confirmar qualquer inconsistência. Para maior segurança, empresas que realizam pagamentos frequentes podem preferir operar seus próprios nós, reduzindo riscos e permitindo uma verificação mais direta e confiável.
9. Combinando e Dividindo Valor
No sistema Bitcoin, cada unidade de valor é tratada como uma "moeda" individual, mas gerenciar cada centavo como uma transação separada seria impraticável. Para resolver isso, o Bitcoin permite que valores sejam combinados ou divididos em transações, facilitando pagamentos de qualquer valor.
Entradas e Saídas
Cada transação no Bitcoin é composta por:
- Entradas: Representam os valores recebidos em transações anteriores.
- Saídas: Correspondem aos valores enviados, divididos entre os destinatários e, eventualmente, o troco para o remetente.
Normalmente, uma transação contém:
- Uma única entrada com valor suficiente para cobrir o pagamento.
- Ou várias entradas combinadas para atingir o valor necessário.
O valor total das saídas nunca excede o das entradas, e a diferença (se houver) pode ser retornada ao remetente como troco.
Exemplo Prático
Imagine que você tem duas entradas:
- 0,03 BTC
- 0,07 BTC
Se deseja enviar 0,08 BTC para alguém, a transação terá:
- Entrada: As duas entradas combinadas (0,03 + 0,07 BTC = 0,10 BTC).
- Saídas: Uma para o destinatário (0,08 BTC) e outra como troco para você (0,02 BTC).
Essa flexibilidade permite que o sistema funcione sem precisar manipular cada unidade mínima individualmente.
Difusão e Simplificação
A difusão de transações, onde uma depende de várias anteriores e assim por diante, não representa um problema. Não é necessário armazenar ou verificar o histórico completo de uma transação para utilizá-la, já que o registro na blockchain garante sua integridade.
10. Privacidade
O modelo bancário tradicional oferece um certo nível de privacidade, limitando o acesso às informações financeiras apenas às partes envolvidas e a um terceiro confiável (como bancos ou instituições financeiras). No entanto, o Bitcoin opera de forma diferente, pois todas as transações são publicamente registradas na blockchain. Apesar disso, a privacidade pode ser mantida utilizando chaves públicas anônimas, que desvinculam diretamente as transações das identidades das partes envolvidas.
Fluxo de Informação
- No modelo tradicional, as transações passam por um terceiro confiável que conhece tanto o remetente quanto o destinatário.
- No Bitcoin, as transações são anunciadas publicamente, mas sem revelar diretamente as identidades das partes. Isso é comparável a dados divulgados por bolsas de valores, onde informações como o tempo e o tamanho das negociações (a "fita") são públicas, mas as identidades das partes não.
Protegendo a Privacidade
Para aumentar a privacidade no Bitcoin, são adotadas as seguintes práticas:
- Chaves Públicas Anônimas: Cada transação utiliza um par de chaves diferentes, dificultando a associação com um proprietário único.
- Prevenção de Ligação: Ao usar chaves novas para cada transação, reduz-se a possibilidade de links evidentes entre múltiplas transações realizadas pelo mesmo usuário.
Riscos de Ligação
Embora a privacidade seja fortalecida, alguns riscos permanecem:
- Transações multi-entrada podem revelar que todas as entradas pertencem ao mesmo proprietário, caso sejam necessárias para somar o valor total.
- O proprietário da chave pode ser identificado indiretamente por transações anteriores que estejam conectadas.
11. Cálculos
Imagine que temos um sistema onde as pessoas (ou computadores) competem para adicionar informações novas (blocos) a um grande registro público (a cadeia de blocos ou blockchain). Este registro é como um livro contábil compartilhado, onde todos podem verificar o que está escrito.
Agora, vamos pensar em um cenário: um atacante quer enganar o sistema. Ele quer mudar informações já registradas para beneficiar a si mesmo, por exemplo, desfazendo um pagamento que já fez. Para isso, ele precisa criar uma versão alternativa do livro contábil (a cadeia de blocos dele) e convencer todos os outros participantes de que essa versão é a verdadeira.
Mas isso é extremamente difícil.
Como o Ataque Funciona
Quando um novo bloco é adicionado à cadeia, ele depende de cálculos complexos que levam tempo e esforço. Esses cálculos são como um grande quebra-cabeça que precisa ser resolvido.
- Os “bons jogadores” (nós honestos) estão sempre trabalhando juntos para resolver esses quebra-cabeças e adicionar novos blocos à cadeia verdadeira.
- O atacante, por outro lado, precisa resolver quebra-cabeças sozinho, tentando “alcançar” a cadeia honesta para que sua versão alternativa pareça válida.
Se a cadeia honesta já está vários blocos à frente, o atacante começa em desvantagem, e o sistema está projetado para que a dificuldade de alcançá-los aumente rapidamente.
A Corrida Entre Cadeias
Você pode imaginar isso como uma corrida. A cada bloco novo que os jogadores honestos adicionam à cadeia verdadeira, eles se distanciam mais do atacante. Para vencer, o atacante teria que resolver os quebra-cabeças mais rápido que todos os outros jogadores honestos juntos.
Suponha que:
- A rede honesta tem 80% do poder computacional (ou seja, resolve 8 de cada 10 quebra-cabeças).
- O atacante tem 20% do poder computacional (ou seja, resolve 2 de cada 10 quebra-cabeças).
Cada vez que a rede honesta adiciona um bloco, o atacante tem que "correr atrás" e resolver mais quebra-cabeças para alcançar.
Por Que o Ataque Fica Cada Vez Mais Improvável?
Vamos usar uma fórmula simples para mostrar como as chances de sucesso do atacante diminuem conforme ele precisa "alcançar" mais blocos:
P = (q/p)^z
- q é o poder computacional do atacante (20%, ou 0,2).
- p é o poder computacional da rede honesta (80%, ou 0,8).
- z é a diferença de blocos entre a cadeia honesta e a cadeia do atacante.
Se o atacante está 5 blocos atrás (z = 5):
P = (0,2 / 0,8)^5 = (0,25)^5 = 0,00098, (ou, 0,098%)
Isso significa que o atacante tem menos de 0,1% de chance de sucesso — ou seja, é muito improvável.
Se ele estiver 10 blocos atrás (z = 10):
P = (0,2 / 0,8)^10 = (0,25)^10 = 0,000000095, (ou, 0,0000095%).
Neste caso, as chances de sucesso são praticamente nulas.
Um Exemplo Simples
Se você jogar uma moeda, a chance de cair “cara” é de 50%. Mas se precisar de 10 caras seguidas, sua chance já é bem menor. Se precisar de 20 caras seguidas, é quase impossível.
No caso do Bitcoin, o atacante precisa de muito mais do que 20 caras seguidas. Ele precisa resolver quebra-cabeças extremamente difíceis e alcançar os jogadores honestos que estão sempre à frente. Isso faz com que o ataque seja inviável na prática.
Por Que Tudo Isso é Seguro?
- A probabilidade de sucesso do atacante diminui exponencialmente. Isso significa que, quanto mais tempo passa, menor é a chance de ele conseguir enganar o sistema.
- A cadeia verdadeira (honesta) está protegida pela força da rede. Cada novo bloco que os jogadores honestos adicionam à cadeia torna mais difícil para o atacante alcançar.
E Se o Atacante Tentar Continuar?
O atacante poderia continuar tentando indefinidamente, mas ele estaria gastando muito tempo e energia sem conseguir nada. Enquanto isso, os jogadores honestos estão sempre adicionando novos blocos, tornando o trabalho do atacante ainda mais inútil.
Assim, o sistema garante que a cadeia verdadeira seja extremamente segura e que ataques sejam, na prática, impossíveis de ter sucesso.
12. Conclusão
Propusemos um sistema de transações eletrônicas que elimina a necessidade de confiança, baseando-se em assinaturas digitais e em uma rede peer-to-peer que utiliza prova de trabalho. Isso resolve o problema do gasto duplo, criando um histórico público de transações imutável, desde que a maioria do poder computacional permaneça sob controle dos participantes honestos. A rede funciona de forma simples e descentralizada, com nós independentes que não precisam de identificação ou coordenação direta. Eles entram e saem livremente, aceitando a cadeia de prova de trabalho como registro do que ocorreu durante sua ausência. As decisões são tomadas por meio do poder de CPU, validando blocos legítimos, estendendo a cadeia e rejeitando os inválidos. Com este mecanismo de consenso, todas as regras e incentivos necessários para o funcionamento seguro e eficiente do sistema são garantidos.
Faça o download do whitepaper original em português: https://bitcoin.org/files/bitcoin-paper/bitcoin_pt_br.pdf
-
 @ f9cf4e94:96abc355
2025-01-18 06:09:50
@ f9cf4e94:96abc355
2025-01-18 06:09:50Para esse exemplo iremos usar: | Nome | Imagem | Descrição | | --------------- | ------------------------------------------------------------ | ------------------------------------------------------------ | | Raspberry PI B+ |
 | Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |
| Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |  | 16Gb |
| 16Gb |Recomendo que use o Ubuntu Server para essa instalação. Você pode baixar o Ubuntu para Raspberry Pi aqui. O passo a passo para a instalação do Ubuntu no Raspberry Pi está disponível aqui. Não instale um desktop (como xubuntu, lubuntu, xfce, etc.).
Passo 1: Atualizar o Sistema 🖥️
Primeiro, atualize seu sistema e instale o Tor:
bash apt update apt install tor
Passo 2: Criar o Arquivo de Serviço
nrs.service🔧Crie o arquivo de serviço que vai gerenciar o servidor Nostr. Você pode fazer isso com o seguinte conteúdo:
```unit [Unit] Description=Nostr Relay Server Service After=network.target
[Service] Type=simple WorkingDirectory=/opt/nrs ExecStart=/opt/nrs/nrs-arm64 Restart=on-failure
[Install] WantedBy=multi-user.target ```
Passo 3: Baixar o Binário do Nostr 🚀
Baixe o binário mais recente do Nostr aqui no GitHub.
Passo 4: Criar as Pastas Necessárias 📂
Agora, crie as pastas para o aplicativo e o pendrive:
bash mkdir -p /opt/nrs /mnt/edriver
Passo 5: Listar os Dispositivos Conectados 🔌
Para saber qual dispositivo você vai usar, liste todos os dispositivos conectados:
bash lsblk
Passo 6: Formatando o Pendrive 💾
Escolha o pendrive correto (por exemplo,
/dev/sda) e formate-o:bash mkfs.vfat /dev/sda
Passo 7: Montar o Pendrive 💻
Monte o pendrive na pasta
/mnt/edriver:bash mount /dev/sda /mnt/edriver
Passo 8: Verificar UUID dos Dispositivos 📋
Para garantir que o sistema monte o pendrive automaticamente, liste os UUID dos dispositivos conectados:
bash blkid
Passo 9: Alterar o
fstabpara Montar o Pendrive Automáticamente 📝Abra o arquivo
/etc/fstabe adicione uma linha para o pendrive, com o UUID que você obteve no passo anterior. A linha deve ficar assim:fstab UUID=9c9008f8-f852 /mnt/edriver vfat defaults 0 0
Passo 10: Copiar o Binário para a Pasta Correta 📥
Agora, copie o binário baixado para a pasta
/opt/nrs:bash cp nrs-arm64 /opt/nrs
Passo 11: Criar o Arquivo de Configuração 🛠️
Crie o arquivo de configuração com o seguinte conteúdo e salve-o em
/opt/nrs/config.yaml:yaml app_env: production info: name: Nostr Relay Server description: Nostr Relay Server pub_key: "" contact: "" url: http://localhost:3334 icon: https://external-content.duckduckgo.com/iu/?u= https://public.bnbstatic.com/image/cms/crawler/COINCU_NEWS/image-495-1024x569.png base_path: /mnt/edriver negentropy: true
Passo 12: Copiar o Serviço para o Diretório de Systemd ⚙️
Agora, copie o arquivo
nrs.servicepara o diretório/etc/systemd/system/:bash cp nrs.service /etc/systemd/system/Recarregue os serviços e inicie o serviço
nrs:bash systemctl daemon-reload systemctl enable --now nrs.service
Passo 13: Configurar o Tor 🌐
Abra o arquivo de configuração do Tor
/var/lib/tor/torrce adicione a seguinte linha:torrc HiddenServiceDir /var/lib/tor/nostr_server/ HiddenServicePort 80 127.0.0.1:3334
Passo 14: Habilitar e Iniciar o Tor 🧅
Agora, ative e inicie o serviço Tor:
bash systemctl enable --now tor.serviceO Tor irá gerar um endereço
.onionpara o seu servidor Nostr. Você pode encontrá-lo no arquivo/var/lib/tor/nostr_server/hostname.
Observações ⚠️
- Com essa configuração, os dados serão salvos no pendrive, enquanto o binário ficará no cartão SD do Raspberry Pi.
- O endereço
.oniondo seu servidor Nostr será algo como:ws://y3t5t5wgwjif<exemplo>h42zy7ih6iwbyd.onion.
Agora, seu servidor Nostr deve estar configurado e funcionando com Tor! 🥳
Se este artigo e as informações aqui contidas forem úteis para você, convidamos a considerar uma doação ao autor como forma de reconhecimento e incentivo à produção de novos conteúdos.
-
 @ 6389be64:ef439d32
2025-01-16 15:44:06
@ 6389be64:ef439d32
2025-01-16 15:44:06Black Locust can grow up to 170 ft tall
Grows 3-4 ft. per year
Native to North America
Cold hardy in zones 3 to 8

Firewood
- BLT wood, on a pound for pound basis is roughly half that of Anthracite Coal
- Since its growth is fast, firewood can be plentiful
Timber

- Rot resistant due to a naturally produced robinin in the wood
- 100 year life span in full soil contact! (better than cedar performance)
- Fence posts
- Outdoor furniture
- Outdoor decking
- Sustainable due to its fast growth and spread
- Can be coppiced (cut to the ground)
- Can be pollarded (cut above ground)
- Its dense wood makes durable tool handles, boxes (tool), and furniture
- The wood is tougher than hickory, which is tougher than hard maple, which is tougher than oak.
- A very low rate of expansion and contraction
- Hardwood flooring
- The highest tensile beam strength of any American tree
- The wood is beautiful
Legume
- Nitrogen fixer
- Fixes the same amount of nitrogen per acre as is needed for 200-bushel/acre corn
- Black walnuts inter-planted with locust as “nurse” trees were shown to rapidly increase their growth [[Clark, Paul M., and Robert D. Williams. (1978) Black walnut growth increased when interplanted with nitrogen-fixing shrubs and trees. Proceedings of the Indiana Academy of Science, vol. 88, pp. 88-91.]]
Bees

- The edible flower clusters are also a top food source for honey bees
Shade Provider

- Its light, airy overstory provides dappled shade
- Planted on the west side of a garden it provides relief during the hottest part of the day
- (nitrogen provider)
- Planted on the west side of a house, its quick growth soon shades that side from the sun
Wind-break

- Fast growth plus it's feathery foliage reduces wind for animals, crops, and shelters
Fodder
- Over 20% crude protein
- 4.1 kcal/g of energy
- Baertsche, S.R, M.T. Yokoyama, and J.W. Hanover (1986) Short rotation, hardwood tree biomass as potential ruminant feed-chemical composition, nylon bag ruminal degradation and ensilement of selected species. J. Animal Sci. 63 2028-2043
-
 @ 6389be64:ef439d32
2025-01-13 21:50:59
@ 6389be64:ef439d32
2025-01-13 21:50:59Bitcoin is more than money, more than an asset, and more than a store of value. Bitcoin is a Prime Mover, an enabler and it ignites imaginations. It certainly fueled an idea in my mind. The idea integrates sensors, computational prowess, actuated machinery, power conversion, and electronic communications to form an autonomous, machined creature roaming forests and harvesting the most widespread and least energy-dense fuel source available. I call it the Forest Walker and it eats wood, and mines Bitcoin.
I know what you're thinking. Why not just put Bitcoin mining rigs where they belong: in a hosted facility sporting electricity from energy-dense fuels like natural gas, climate-controlled with excellent data piping in and out? Why go to all the trouble building a robot that digests wood creating flammable gasses fueling an engine to run a generator powering Bitcoin miners? It's all about synergy.
Bitcoin mining enables the realization of multiple, seemingly unrelated, yet useful activities. Activities considered un-profitable if not for Bitcoin as the Prime Mover. This is much more than simply mining the greatest asset ever conceived by humankind. It’s about the power of synergy, which Bitcoin plays only one of many roles. The synergy created by this system can stabilize forests' fire ecology while generating multiple income streams. That’s the realistic goal here and requires a brief history of American Forest management before continuing.
Smokey The Bear
In 1944, the Smokey Bear Wildfire Prevention Campaign began in the United States. “Only YOU can prevent forest fires” remains the refrain of the Ad Council’s longest running campaign. The Ad Council is a U.S. non-profit set up by the American Association of Advertising Agencies and the Association of National Advertisers in 1942. It would seem that the U.S. Department of the Interior was concerned about pesky forest fires and wanted them to stop. So, alongside a national policy of extreme fire suppression they enlisted the entire U.S. population to get onboard via the Ad Council and it worked. Forest fires were almost obliterated and everyone was happy, right? Wrong.
Smokey is a fantastically successful bear so forest fires became so few for so long that the fuel load - dead wood - in forests has become very heavy. So heavy that when a fire happens (and they always happen) it destroys everything in its path because the more fuel there is the hotter that fire becomes. Trees, bushes, shrubs, and all other plant life cannot escape destruction (not to mention homes and businesses). The soil microbiology doesn’t escape either as it is burned away even in deeper soils. To add insult to injury, hydrophobic waxy residues condense on the soil surface, forcing water to travel over the ground rather than through it eroding forest soils. Good job, Smokey. Well done, Sir!
Most terrestrial ecologies are “fire ecologies”. Fire is a part of these systems’ fuel load and pest management. Before we pretended to “manage” millions of acres of forest, fires raged over the world, rarely damaging forests. The fuel load was always too light to generate fires hot enough to moonscape mountainsides. Fires simply burned off the minor amounts of fuel accumulated since the fire before. The lighter heat, smoke, and other combustion gasses suppressed pests, keeping them in check and the smoke condensed into a plant growth accelerant called wood vinegar, not a waxy cap on the soil. These fires also cleared out weak undergrowth, cycled minerals, and thinned the forest canopy, allowing sunlight to penetrate to the forest floor. Without a fire’s heat, many pine tree species can’t sow their seed. The heat is required to open the cones (the seed bearing structure) of Spruce, Cypress, Sequoia, Jack Pine, Lodgepole Pine and many more. Without fire forests can’t have babies. The idea was to protect the forests, and it isn't working.
So, in a world of fire, what does an ally look like and what does it do?
Meet The Forest Walker
For the Forest Walker to work as a mobile, autonomous unit, a solid platform that can carry several hundred pounds is required. It so happens this chassis already exists but shelved.
Introducing the Legged Squad Support System (LS3). A joint project between Boston Dynamics, DARPA, and the United States Marine Corps, the quadrupedal robot is the size of a cow, can carry 400 pounds (180 kg) of equipment, negotiate challenging terrain, and operate for 24 hours before needing to refuel. Yes, it had an engine. Abandoned in 2015, the thing was too noisy for military deployment and maintenance "under fire" is never a high-quality idea. However, we can rebuild it to act as a platform for the Forest Walker; albeit with serious alterations. It would need to be bigger, probably. Carry more weight? Definitely. Maybe replace structural metal with carbon fiber and redesign much as 3D printable parts for more effective maintenance.
The original system has a top operational speed of 8 miles per hour. For our purposes, it only needs to move about as fast as a grazing ruminant. Without the hammering vibrations of galloping into battle, shocks of exploding mortars, and drunken soldiers playing "Wrangler of Steel Machines", time between failures should be much longer and the overall energy consumption much lower. The LS3 is a solid platform to build upon. Now it just needs to be pulled out of the mothballs, and completely refitted with outboard equipment.
The Small Branch Chipper
When I say “Forest fuel load” I mean the dead, carbon containing litter on the forest floor. Duff (leaves), fine-woody debris (small branches), and coarse woody debris (logs) are the fuel that feeds forest fires. Walk through any forest in the United States today and you will see quite a lot of these materials. Too much, as I have described. Some of these fuel loads can be 8 tons per acre in pine and hardwood forests and up to 16 tons per acre at active logging sites. That’s some big wood and the more that collects, the more combustible danger to the forest it represents. It also provides a technically unlimited fuel supply for the Forest Walker system.
The problem is that this detritus has to be chewed into pieces that are easily ingestible by the system for the gasification process (we’ll get to that step in a minute). What we need is a wood chipper attached to the chassis (the LS3); its “mouth”.
A small wood chipper handling material up to 2.5 - 3.0 inches (6.3 - 7.6 cm) in diameter would eliminate a substantial amount of fuel. There is no reason for Forest Walker to remove fallen trees. It wouldn’t have to in order to make a real difference. It need only identify appropriately sized branches and grab them. Once loaded into the chipper’s intake hopper for further processing, the beast can immediately look for more “food”. This is essentially kindling that would help ignite larger logs. If it’s all consumed by Forest Walker, then it’s not present to promote an aggravated conflagration.
I have glossed over an obvious question: How does Forest Walker see and identify branches and such? LiDaR (Light Detection and Ranging) attached to Forest Walker images the local area and feed those data to onboard computers for processing. Maybe AI plays a role. Maybe simple machine learning can do the trick. One thing is for certain: being able to identify a stick and cause robotic appendages to pick it up is not impossible.
Great! We now have a quadrupedal robot autonomously identifying and “eating” dead branches and other light, combustible materials. Whilst strolling through the forest, depleting future fires of combustibles, Forest Walker has already performed a major function of this system: making the forest safer. It's time to convert this low-density fuel into a high-density fuel Forest Walker can leverage. Enter the gasification process.
The Gassifier
The gasifier is the heart of the entire system; it’s where low-density fuel becomes the high-density fuel that powers the entire system. Biochar and wood vinegar are process wastes and I’ll discuss why both are powerful soil amendments in a moment, but first, what’s gasification?
Reacting shredded carbonaceous material at high temperatures in a low or no oxygen environment converts the biomass into biochar, wood vinegar, heat, and Synthesis Gas (Syngas). Syngas consists primarily of hydrogen, carbon monoxide, and methane. All of which are extremely useful fuels in a gaseous state. Part of this gas is used to heat the input biomass and keep the reaction temperature constant while the internal combustion engine that drives the generator to produce electrical power consumes the rest.
Critically, this gasification process is “continuous feed”. Forest Walker must intake biomass from the chipper, process it to fuel, and dump the waste (CO2, heat, biochar, and wood vinegar) continuously. It cannot stop. Everything about this system depends upon this continual grazing, digestion, and excretion of wastes just as a ruminal does. And, like a ruminant, all waste products enhance the local environment.
When I first heard of gasification, I didn’t believe that it was real. Running an electric generator from burning wood seemed more akin to “conspiracy fantasy” than science. Not only is gasification real, it’s ancient technology. A man named Dean Clayton first started experiments on gasification in 1699 and in 1901 gasification was used to power a vehicle. By the end of World War II, there were 500,000 Syngas powered vehicles in Germany alone because of fossil fuel rationing during the war. The global gasification market was $480 billion in 2022 and projected to be as much as $700 billion by 2030 (Vantage Market Research). Gasification technology is the best choice to power the Forest Walker because it’s self-contained and we want its waste products.
Biochar: The Waste
Biochar (AKA agricultural charcoal) is fairly simple: it’s almost pure, solid carbon that resembles charcoal. Its porous nature packs large surface areas into small, 3 dimensional nuggets. Devoid of most other chemistry, like hydrocarbons (methane) and ash (minerals), biochar is extremely lightweight. Do not confuse it with the charcoal you buy for your grill. Biochar doesn’t make good grilling charcoal because it would burn too rapidly as it does not contain the multitude of flammable components that charcoal does. Biochar has several other good use cases. Water filtration, water retention, nutrient retention, providing habitat for microscopic soil organisms, and carbon sequestration are the main ones that we are concerned with here.
Carbon has an amazing ability to adsorb (substances stick to and accumulate on the surface of an object) manifold chemistries. Water, nutrients, and pollutants tightly bind to carbon in this format. So, biochar makes a respectable filter and acts as a “battery” of water and nutrients in soils. Biochar adsorbs and holds on to seven times its weight in water. Soil containing biochar is more drought resilient than soil without it. Adsorbed nutrients, tightly sequestered alongside water, get released only as plants need them. Plants must excrete protons (H+) from their roots to disgorge water or positively charged nutrients from the biochar's surface; it's an active process.
Biochar’s surface area (where adsorption happens) can be 500 square meters per gram or more. That is 10% larger than an official NBA basketball court for every gram of biochar. Biochar’s abundant surface area builds protective habitats for soil microbes like fungi and bacteria and many are critical for the health and productivity of the soil itself.
The “carbon sequestration” component of biochar comes into play where “carbon credits” are concerned. There is a financial market for carbon. Not leveraging that market for revenue is foolish. I am climate agnostic. All I care about is that once solid carbon is inside the soil, it will stay there for thousands of years, imparting drought resiliency, fertility collection, nutrient buffering, and release for that time span. I simply want as much solid carbon in the soil because of the undeniably positive effects it has, regardless of any climactic considerations.
Wood Vinegar: More Waste
Another by-product of the gasification process is wood vinegar (Pyroligneous acid). If you have ever seen Liquid Smoke in the grocery store, then you have seen wood vinegar. Principally composed of acetic acid, acetone, and methanol wood vinegar also contains ~200 other organic compounds. It would seem intuitive that condensed, liquefied wood smoke would at least be bad for the health of all living things if not downright carcinogenic. The counter intuition wins the day, however. Wood vinegar has been used by humans for a very long time to promote digestion, bowel, and liver health; combat diarrhea and vomiting; calm peptic ulcers and regulate cholesterol levels; and a host of other benefits.
For centuries humans have annually burned off hundreds of thousands of square miles of pasture, grassland, forest, and every other conceivable terrestrial ecosystem. Why is this done? After every burn, one thing becomes obvious: the almost supernatural growth these ecosystems exhibit after the burn. How? Wood vinegar is a component of this growth. Even in open burns, smoke condenses and infiltrates the soil. That is when wood vinegar shows its quality.
This stuff beefs up not only general plant growth but seed germination as well and possesses many other qualities that are beneficial to plants. It’s a pesticide, fungicide, promotes beneficial soil microorganisms, enhances nutrient uptake, and imparts disease resistance. I am barely touching a long list of attributes here, but you want wood vinegar in your soil (alongside biochar because it adsorbs wood vinegar as well).
The Internal Combustion Engine
Conversion of grazed forage to chemical, then mechanical, and then electrical energy completes the cycle. The ICE (Internal Combustion Engine) converts the gaseous fuel output from the gasifier to mechanical energy, heat, water vapor, and CO2. It’s the mechanical energy of a rotating drive shaft that we want. That rotation drives the electric generator, which is the heartbeat we need to bring this monster to life. Luckily for us, combined internal combustion engine and generator packages are ubiquitous, delivering a defined energy output given a constant fuel input. It’s the simplest part of the system.
The obvious question here is whether the amount of syngas provided by the gasification process will provide enough energy to generate enough electrons to run the entire system or not. While I have no doubt the energy produced will run Forest Walker's main systems the question is really about the electrons left over. Will it be enough to run the Bitcoin mining aspect of the system? Everything is a budget.
CO2 Production For Growth
Plants are lollipops. No matter if it’s a tree or a bush or a shrubbery, the entire thing is mostly sugar in various formats but mostly long chain carbohydrates like lignin and cellulose. Plants need three things to make sugar: CO2, H2O and light. In a forest, where tree densities can be quite high, CO2 availability becomes a limiting growth factor. It’d be in the forest interests to have more available CO2 providing for various sugar formation providing the organism with food and structure.
An odd thing about tree leaves, the openings that allow gasses like the ever searched for CO2 are on the bottom of the leaf (these are called stomata). Not many stomata are topside. This suggests that trees and bushes have evolved to find gasses like CO2 from below, not above and this further suggests CO2 might be in higher concentrations nearer the soil.
The soil life (bacterial, fungi etc.) is constantly producing enormous amounts of CO2 and it would stay in the soil forever (eventually killing the very soil life that produces it) if not for tidal forces. Water is everywhere and whether in pools, lakes, oceans or distributed in “moist” soils water moves towards to the moon. The water in the soil and also in the water tables below the soil rise toward the surface every day. When the water rises, it expels the accumulated gasses in the soil into the atmosphere and it’s mostly CO2. It’s a good bet on how leaves developed high populations of stomata on the underside of leaves. As the water relaxes (the tide goes out) it sucks oxygenated air back into the soil to continue the functions of soil life respiration. The soil “breathes” albeit slowly.
The gasses produced by the Forest Walker’s internal combustion engine consist primarily of CO2 and H2O. Combusting sugars produce the same gasses that are needed to construct the sugars because the universe is funny like that. The Forest Walker is constantly laying down these critical construction elements right where the trees need them: close to the ground to be gobbled up by the trees.
The Branch Drones
During the last ice age, giant mammals populated North America - forests and otherwise. Mastodons, woolly mammoths, rhinos, short-faced bears, steppe bison, caribou, musk ox, giant beavers, camels, gigantic ground-dwelling sloths, glyptodons, and dire wolves were everywhere. Many were ten to fifteen feet tall. As they crashed through forests, they would effectively cleave off dead side-branches of trees, halting the spread of a ground-based fire migrating into the tree crown ("laddering") which is a death knell for a forest.
These animals are all extinct now and forests no longer have any manner of pruning services. But, if we build drones fitted with cutting implements like saws and loppers, optical cameras and AI trained to discern dead branches from living ones, these drones could effectively take over pruning services by identifying, cutting, and dropping to the forest floor, dead branches. The dropped branches simply get collected by the Forest Walker as part of its continual mission.
The drones dock on the back of the Forest Walker to recharge their batteries when low. The whole scene would look like a grazing cow with some flies bothering it. This activity breaks the link between a relatively cool ground based fire and the tree crowns and is a vital element in forest fire control.
The Bitcoin Miner
Mining is one of four monetary incentive models, making this system a possibility for development. The other three are US Dept. of the Interior, township, county, and electrical utility company easement contracts for fuel load management, global carbon credits trading, and data set sales. All the above depends on obvious questions getting answered. I will list some obvious ones, but this is not an engineering document and is not the place for spreadsheets. How much Bitcoin one Forest Walker can mine depends on everything else. What amount of biomass can we process? Will that biomass flow enough Syngas to keep the lights on? Can the chassis support enough mining ASICs and supporting infrastructure? What does that weigh and will it affect field performance? How much power can the AC generator produce?
Other questions that are more philosophical persist. Even if a single Forest Walker can only mine scant amounts of BTC per day, that pales to how much fuel material it can process into biochar. We are talking about millions upon millions of forested acres in need of fuel load management. What can a single Forest Walker do? I am not thinking in singular terms. The Forest Walker must operate as a fleet. What could 50 do? 500?
What is it worth providing a service to the world by managing forest fuel loads? Providing proof of work to the global monetary system? Seeding soil with drought and nutrient resilience by the excretion, over time, of carbon by the ton? What did the last forest fire cost?
The Mesh Network
What could be better than one bitcoin mining, carbon sequestering, forest fire squelching, soil amending behemoth? Thousands of them, but then they would need to be able to talk to each other to coordinate position, data handling, etc. Fitted with a mesh networking device, like goTenna or Meshtastic LoRa equipment enables each Forest Walker to communicate with each other.
Now we have an interconnected fleet of Forest Walkers relaying data to each other and more importantly, aggregating all of that to the last link in the chain for uplink. Well, at least Bitcoin mining data. Since block data is lightweight, transmission of these data via mesh networking in fairly close quartered environs is more than doable. So, how does data transmit to the Bitcoin Network? How do the Forest Walkers get the previous block data necessary to execute on mining?
Back To The Chain
Getting Bitcoin block data to and from the network is the last puzzle piece. The standing presumption here is that wherever a Forest Walker fleet is operating, it is NOT within cell tower range. We further presume that the nearest Walmart Wi-Fi is hours away. Enter the Blockstream Satellite or something like it.
A separate, ground-based drone will have two jobs: To stay as close to the nearest Forest Walker as it can and to provide an antennae for either terrestrial or orbital data uplink. Bitcoin-centric data is transmitted to the "uplink drone" via the mesh networked transmitters and then sent on to the uplink and the whole flow goes in the opposite direction as well; many to one and one to many.
We cannot transmit data to the Blockstream satellite, and it will be up to Blockstream and companies like it to provide uplink capabilities in the future and I don't doubt they will. Starlink you say? What’s stopping that company from filtering out block data? Nothing because it’s Starlink’s system and they could decide to censor these data. It seems we may have a problem sending and receiving Bitcoin data in back country environs.
But, then again, the utility of this system in staunching the fuel load that creates forest fires is extremely useful around forested communities and many have fiber, Wi-Fi and cell towers. These communities could be a welcoming ground zero for first deployments of the Forest Walker system by the home and business owners seeking fire repression. In the best way, Bitcoin subsidizes the safety of the communities.
Sensor Packages
LiDaR
The benefit of having a Forest Walker fleet strolling through the forest is the never ending opportunity for data gathering. A plethora of deployable sensors gathering hyper-accurate data on everything from temperature to topography is yet another revenue generator. Data is valuable and the Forest Walker could generate data sales to various government entities and private concerns.
LiDaR (Light Detection and Ranging) can map topography, perform biomass assessment, comparative soil erosion analysis, etc. It so happens that the Forest Walker’s ability to “see,” to navigate about its surroundings, is LiDaR driven and since it’s already being used, we can get double duty by harvesting that data for later use. By using a laser to send out light pulses and measuring the time it takes for the reflection of those pulses to return, very detailed data sets incrementally build up. Eventually, as enough data about a certain area becomes available, the data becomes useful and valuable.
Forestry concerns, both private and public, often use LiDaR to build 3D models of tree stands to assess the amount of harvest-able lumber in entire sections of forest. Consulting companies offering these services charge anywhere from several hundred to several thousand dollars per square kilometer for such services. A Forest Walker generating such assessments on the fly while performing its other functions is a multi-disciplinary approach to revenue generation.
pH, Soil Moisture, and Cation Exchange Sensing
The Forest Walker is quadrupedal, so there are four contact points to the soil. Why not get a pH data point for every step it takes? We can also gather soil moisture data and cation exchange capacities at unheard of densities because of sampling occurring on the fly during commission of the system’s other duties. No one is going to build a machine to do pH testing of vast tracts of forest soils, but that doesn’t make the data collected from such an endeavor valueless. Since the Forest Walker serves many functions at once, a multitude of data products can add to the return on investment component.
Weather Data
Temperature, humidity, pressure, and even data like evapotranspiration gathered at high densities on broad acre scales have untold value and because the sensors are lightweight and don’t require large power budgets, they come along for the ride at little cost. But, just like the old mantra, “gas, grass, or ass, nobody rides for free”, these sensors provide potential revenue benefits just by them being present.
I’ve touched on just a few data genres here. In fact, the question for universities, governmental bodies, and other institutions becomes, “How much will you pay us to attach your sensor payload to the Forest Walker?”
Noise Suppression
Only you can prevent Metallica filling the surrounds with 120 dB of sound. Easy enough, just turn the car stereo off. But what of a fleet of 50 Forest Walkers operating in the backcountry or near a township? 500? 5000? Each one has a wood chipper, an internal combustion engine, hydraulic pumps, actuators, and more cooling fans than you can shake a stick at. It’s a walking, screaming fire-breathing dragon operating continuously, day and night, twenty-four hours a day, three hundred sixty-five days a year. The sound will negatively affect all living things and that impacts behaviors. Serious engineering consideration and prowess must deliver a silencing blow to the major issue of noise.
It would be foolish to think that a fleet of Forest Walkers could be silent, but if not a major design consideration, then the entire idea is dead on arrival. Townships would not allow them to operate even if they solved the problem of widespread fuel load and neither would governmental entities, and rightly so. Nothing, not man nor beast, would want to be subjected to an eternal, infernal scream even if it were to end within days as the fleet moved further away after consuming what it could. Noise and heat are the only real pollutants of this system; taking noise seriously from the beginning is paramount.
Fire Safety
A “fire-breathing dragon” is not the worst description of the Forest Walker. It eats wood, combusts it at very high temperatures and excretes carbon; and it does so in an extremely flammable environment. Bad mix for one Forest Walker, worse for many. One must take extreme pains to ensure that during normal operation, a Forest Walker could fall over, walk through tinder dry brush, or get pounded into the ground by a meteorite from Krypton and it wouldn’t destroy epic swaths of trees and baby deer. I envision an ultimate test of a prototype to include dowsing it in grain alcohol while it’s wrapped up in toilet paper like a pledge at a fraternity party. If it runs for 72 hours and doesn’t set everything on fire, then maybe outside entities won’t be fearful of something that walks around forests with a constant fire in its belly.
The Wrap
How we think about what can be done with and adjacent to Bitcoin is at least as important as Bitcoin’s economic standing itself. For those who will tell me that this entire idea is without merit, I say, “OK, fine. You can come up with something, too.” What can we plug Bitcoin into that, like a battery, makes something that does not work, work? That’s the lesson I get from this entire exercise. No one was ever going to hire teams of humans to go out and "clean the forest". There's no money in that. The data collection and sales from such an endeavor might provide revenues over the break-even point but investment demands Alpha in this day and age. But, plug Bitcoin into an almost viable system and, voilà! We tip the scales to achieve lift-off.
Let’s face it, we haven’t scratched the surface of Bitcoin’s forcing function on our minds. Not because it’s Bitcoin, but because of what that invention means. The question that pushes me to approach things this way is, “what can we create that one system’s waste is another system’s feedstock?” The Forest Walker system’s only real waste is the conversion of low entropy energy (wood and syngas) into high entropy energy (heat and noise). All other output is beneficial to humanity.
Bitcoin, I believe, is the first product of a new mode of human imagination. An imagination newly forged over the past few millennia of being lied to, stolen from, distracted and otherwise mis-allocated to a black hole of the nonsensical. We are waking up.
What I have presented is not science fiction. Everything I have described here is well within the realm of possibility. The question is one of viability, at least in terms of the detritus of the old world we find ourselves departing from. This system would take a non-trivial amount of time and resources to develop. I think the system would garner extensive long-term contracts from those who have the most to lose from wildfires, the most to gain from hyperaccurate data sets, and, of course, securing the most precious asset in the world. Many may not see it that way, for they seek Alpha and are therefore blind to other possibilities. Others will see only the possibilities; of thinking in a new way, of looking at things differently, and dreaming of what comes next.
-
 @ e3ba5e1a:5e433365
2025-01-13 16:47:27
@ e3ba5e1a:5e433365
2025-01-13 16:47:27My blog posts and reading material have both been on a decidedly economics-heavy slant recently. The topic today, incentives, squarely falls into the category of economics. However, when I say economics, I’m not talking about “analyzing supply and demand curves.” I’m talking about the true basis of economics: understanding how human beings make decisions in a world of scarcity.
A fair definition of incentive is “a reward or punishment that motivates behavior to achieve a desired outcome.” When most people think about economic incentives, they’re thinking of money. If I offer my son $5 if he washes the dishes, I’m incentivizing certain behavior. We can’t guarantee that he’ll do what I want him to do, but we can agree that the incentive structure itself will guide and ultimately determine what outcome will occur.
The great thing about monetary incentives is how easy they are to talk about and compare. “Would I rather make $5 washing the dishes or $10 cleaning the gutters?” But much of the world is incentivized in non-monetary ways too. For example, using the “punishment” half of the definition above, I might threaten my son with losing Nintendo Switch access if he doesn’t wash the dishes. No money is involved, but I’m still incentivizing behavior.
And there are plenty of incentives beyond our direct control! My son is also incentivized to not wash dishes because it’s boring, or because he has some friends over that he wants to hang out with, or dozens of other things. Ultimately, the conflicting array of different incentive structures placed on him will ultimately determine what actions he chooses to take.
Why incentives matter
A phrase I see often in discussions—whether they are political, parenting, economic, or business—is “if they could just do…” Each time I see that phrase, I cringe a bit internally. Usually, the underlying assumption of the statement is “if people would behave contrary to their incentivized behavior then things would be better.” For example:
- If my kids would just go to bed when I tell them, they wouldn’t be so cranky in the morning.
- If people would just use the recycling bin, we wouldn’t have such a landfill problem.
- If people would just stop being lazy, our team would deliver our project on time.
In all these cases, the speakers are seemingly flummoxed as to why the people in question don’t behave more rationally. The problem is: each group is behaving perfectly rationally.
- The kids have a high time preference, and care more about the joy of staying up now than the crankiness in the morning. Plus, they don’t really suffer the consequences of morning crankiness, their parents do.
- No individual suffers much from their individual contribution to a landfill. If they stopped growing the size of the landfill, it would make an insignificant difference versus the amount of effort they need to engage in to properly recycle.
- If a team doesn’t properly account for the productivity of individuals on a project, each individual receives less harm from their own inaction. Sure, the project may be delayed, company revenue may be down, and they may even risk losing their job when the company goes out of business. But their laziness individually won’t determine the entirety of that outcome. By contrast, they greatly benefit from being lazy by getting to relax at work, go on social media, read a book, or do whatever else they do when they’re supposed to be working.

My point here is that, as long as you ignore the reality of how incentives drive human behavior, you’ll fail at getting the outcomes you want.
If everything I wrote up until now made perfect sense, you understand the premise of this blog post. The rest of it will focus on a bunch of real-world examples to hammer home the point, and demonstrate how versatile this mental model is.
Running a company
Let’s say I run my own company, with myself as the only employee. My personal revenue will be 100% determined by my own actions. If I decide to take Tuesday afternoon off and go fishing, I’ve chosen to lose that afternoon’s revenue. Implicitly, I’ve decided that the enjoyment I get from an afternoon of fishing is greater than the potential revenue. You may think I’m being lazy, but it’s my decision to make. In this situation, the incentive–money–is perfectly aligned with my actions.
Compare this to a typical company/employee relationship. I might have a bank of Paid Time Off (PTO) days, in which case once again my incentives are relatively aligned. I know that I can take off 15 days throughout the year, and I’ve chosen to use half a day for the fishing trip. All is still good.
What about unlimited time off? Suddenly incentives are starting to misalign. I don’t directly pay a price for not showing up to work on Tuesday. Or Wednesday as well, for that matter. I might ultimately be fired for not doing my job, but that will take longer to work its way through the system than simply not making any money for the day taken off.
Compensation overall falls into this misaligned incentive structure. Let’s forget about taking time off. Instead, I work full time on a software project I’m assigned. But instead of using the normal toolchain we’re all used to at work, I play around with a new programming language. I get the fun and joy of playing with new technology, and potentially get to pad my resume a bit when I’m ready to look for a new job. But my current company gets slower results, less productivity, and is forced to subsidize my extracurricular learning.
When a CEO has a bonus structure based on profitability, he’ll do everything he can to make the company profitable. This might include things that actually benefit the company, like improving product quality, reducing internal red tape, or finding cheaper vendors. But it might also include destructive practices, like slashing the R\&D budget to show massive profits this year, in exchange for a catastrophe next year when the next version of the product fails to ship.

Or my favorite example. My parents owned a business when I was growing up. They had a back office where they ran operations like accounting. All of the furniture was old couches from our house. After all, any money they spent on furniture came right out of their paychecks! But in a large corporate environment, each department is generally given a budget for office furniture, a budget which doesn’t roll over year-to-year. The result? Executives make sure to spend the entire budget each year, often buying furniture far more expensive than they would choose if it was their own money.
There are plenty of details you can quibble with above. It’s in a company’s best interest to give people downtime so that they can come back recharged. Having good ergonomic furniture can in fact increase productivity in excess of the money spent on it. But overall, the picture is pretty clear: in large corporate structures, you’re guaranteed to have mismatches between the company’s goals and the incentive structure placed on individuals.
Using our model from above, we can lament how lazy, greedy, and unethical the employees are for doing what they’re incentivized to do instead of what’s right. But that’s simply ignoring the reality of human nature.
Moral hazard
Moral hazard is a situation where one party is incentivized to take on more risk because another party will bear the consequences. Suppose I tell my son when he turns 21 (or whatever legal gambling age is) that I’ll cover all his losses for a day at the casino, but he gets to keep all the winnings.
What do you think he’s going to do? The most logical course of action is to place the largest possible bets for as long as possible, asking me to cover each time he loses, and taking money off the table and into his bank account each time he wins.

But let’s look at a slightly more nuanced example. I go to a bathroom in the mall. As I’m leaving, I wash my hands. It will take me an extra 1 second to turn off the water when I’m done washing. That’s a trivial price to pay. If I don’t turn off the water, the mall will have to pay for many liters of wasted water, benefiting no one. But I won’t suffer any consequences at all.
This is also a moral hazard, but most people will still turn off the water. Why? Usually due to some combination of other reasons such as:
- We’re so habituated to turning off the water that we don’t even consider not turning it off. Put differently, the mental effort needed to not turn off the water is more expensive than the 1 second of time to turn it off.
- Many of us have been brought up with a deep guilt about wasting resources like water. We have an internal incentive structure that makes the 1 second to turn off the water much less costly than the mental anguish of the waste we created.
- We’re afraid we’ll be caught by someone else and face some kind of social repercussions. (Or maybe more than social. Are you sure there isn’t a law against leaving the water tap on?)
Even with all that in place, you may notice that many public bathrooms use automatic water dispensers. Sure, there’s a sanitation reason for that, but it’s also to avoid this moral hazard.
A common denominator in both of these is that the person taking the action that causes the liability (either the gambling or leaving the water on) is not the person who bears the responsibility for that liability (the father or the mall owner). Generally speaking, the closer together the person making the decision and the person incurring the liability are, the smaller the moral hazard.
It’s easy to demonstrate that by extending the casino example a bit. I said it was the father who was covering the losses of the gambler. Many children (though not all) would want to avoid totally bankrupting their parents, or at least financially hurting them. Instead, imagine that someone from the IRS shows up at your door, hands you a credit card, and tells you you can use it at a casino all day, taking home all the chips you want. The money is coming from the government. How many people would put any restriction on how much they spend?
And since we’re talking about the government already…
Government moral hazards
As I was preparing to write this blog post, the California wildfires hit. The discussions around those wildfires gave a huge number of examples of moral hazards. I decided to cherry-pick a few for this post.
The first and most obvious one: California is asking for disaster relief funds from the federal government. That sounds wonderful. These fires were a natural disaster, so why shouldn’t the federal government pitch in and help take care of people?
The problem is, once again, a moral hazard. In the case of the wildfires, California and Los Angeles both had ample actions they could have taken to mitigate the destruction of this fire: better forest management, larger fire department, keeping the water reservoirs filled, and probably much more that hasn’t come to light yet.
If the federal government bails out California, it will be a clear message for the future: your mistakes will be fixed by others. You know what kind of behavior that incentivizes? More risky behavior! Why spend state funds on forest management and extra firefighters—activities that don’t win politicians a lot of votes in general—when you could instead spend it on a football stadium, higher unemployment payments, or anything else, and then let the feds cover the cost of screw-ups.
You may notice that this is virtually identical to the 2008 “too big to fail” bail-outs. Wall Street took insanely risky behavior, reaped huge profits for years, and when they eventually got caught with their pants down, the rest of us bailed them out. “Privatizing profits, socializing losses.”

And here’s the absolute best part of this: I can’t even truly blame either California or Wall Street. (I mean, I do blame them, I think their behavior is reprehensible, but you’ll see what I mean.) In a world where the rules of the game implicitly include the bail-out mentality, you would be harming your citizens/shareholders/investors if you didn’t engage in that risky behavior. Since everyone is on the hook for those socialized losses, your best bet is to maximize those privatized profits.
There’s a lot more to government and moral hazard, but I think these two cases demonstrate the crux pretty solidly. But let’s leave moral hazard behind for a bit and get to general incentivization discussions.
Non-monetary competition
At least 50% of the economics knowledge I have comes from the very first econ course I took in college. That professor was amazing, and had some very colorful stories. I can’t vouch for the veracity of the two I’m about to share, but they definitely drive the point home.
In the 1970s, the US had an oil shortage. To “fix” this problem, they instituted price caps on gasoline, which of course resulted in insufficient gasoline. To “fix” this problem, they instituted policies where, depending on your license plate number, you could only fill up gas on certain days of the week. (Irrelevant detail for our point here, but this just resulted in people filling up their tanks more often, no reduction in gas usage.)
Anyway, my professor’s wife had a friend. My professor described in great detail how attractive this woman was. I’ll skip those details here since this is a PG-rated blog. In any event, she never had any trouble filling up her gas tank any day of the week. She would drive up, be told she couldn’t fill up gas today, bat her eyes at the attendant, explain how helpless she was, and was always allowed to fill up gas.
This is a demonstration of non-monetary compensation. Most of the time in a free market, capitalist economy, people are compensated through money. When price caps come into play, there’s a limit to how much monetary compensation someone can receive. And in that case, people find other ways of competing. Like this woman’s case: through using flirtatious behavior to compensate the gas station workers to let her cheat the rules.
The other example was much more insidious. Santa Monica had a problem: it was predominantly wealthy and white. They wanted to fix this problem, and decided to put in place rent controls. After some time, they discovered that Santa Monica had become wealthier and whiter, the exact opposite of their desired outcome. Why would that happen?
Someone investigated, and ended up interviewing a landlady that demonstrated the reason. She was an older white woman, and admittedly racist. Prior to the rent controls, she would list her apartments in the newspaper, and would be legally obligated to rent to anyone who could afford it. Once rent controls were in place, she took a different tact. She knew that she would only get a certain amount for the apartment, and that the demand for apartments was higher than the supply. That meant she could be picky.
She ended up finding tenants through friends-of-friends. Since it wasn’t an official advertisement, she wasn’t legally required to rent it out if someone could afford to pay. Instead, she got to interview people individually and then make them an offer. Normally, that would have resulted in receiving a lower rental price, but not under rent controls.
So who did she choose? A young, unmarried, wealthy, white woman. It made perfect sense. Women were less intimidating and more likely to maintain the apartment better. Wealthy people, she determined, would be better tenants. (I have no idea if this is true in practice or not, I’m not a landlord myself.) Unmarried, because no kids running around meant less damage to the property. And, of course, white. Because she was racist, and her incentive structure made her prefer whites.
You can deride her for being racist, I won’t disagree with you. But it’s simply the reality. Under the non-rent-control scenario, her profit motive for money outweighed her racism motive. But under rent control, the monetary competition was removed, and she was free to play into her racist tendencies without facing any negative consequences.
Bureaucracy
These were the two examples I remember for that course. But non-monetary compensation pops up in many more places. One highly pertinent example is bureaucracies. Imagine you have a government office, or a large corporation’s acquisition department, or the team that apportions grants at a university. In all these cases, you have a group of people making decisions about handing out money that has no monetary impact on them. If they give to the best qualified recipients, they receive no raises. If they spend the money recklessly on frivolous projects, they face no consequences.
Under such an incentivization scheme, there’s little to encourage the bureaucrats to make intelligent funding decisions. Instead, they’ll be incentivized to spend the money where they recognize non-monetary benefits. This is why it’s so common to hear about expensive meals, gift bags at conferences, and even more inappropriate ways of trying to curry favor with those that hold the purse strings.
Compare that ever so briefly with the purchases made by a small mom-and-pop store like my parents owned. Could my dad take a bribe to buy from a vendor who’s ripping him off? Absolutely he could! But he’d lose more on the deal than he’d make on the bribe, since he’s directly incentivized by the deal itself. It would make much more sense for him to go with the better vendor, save $5,000 on the deal, and then treat himself to a lavish $400 meal to celebrate.
Government incentivized behavior
This post is getting longer in the tooth than I’d intended, so I’ll finish off with this section and make it a bit briefer. Beyond all the methods mentioned above, government has another mechanism for modifying behavior: through directly changing incentives via legislation, regulation, and monetary policy. Let’s see some examples:
- Artificial modification of interest rates encourages people to take on more debt than they would in a free capital market, leading to malinvestment and a consumer debt crisis, and causing the boom-bust cycle we all painfully experience.
- Going along with that, giving tax breaks on interest payments further artificially incentivizes people to take on debt that they wouldn’t otherwise.
- During COVID-19, at some points unemployment benefits were greater than minimum wage, incentivizing people to rather stay home and not work than get a job, leading to reduced overall productivity in the economy and more printed dollars for benefits. In other words, it was a perfect recipe for inflation.
- The tax code gives deductions to “help” people. That might be true, but the real impact is incentivizing people to make decisions they wouldn’t have otherwise. For example, giving out tax deductions on children encourages having more kids. Tax deductions on childcare and preschools incentivizes dual-income households. Whether or not you like the outcomes, it’s clear that it’s government that’s encouraging these outcomes to happen.
- Tax incentives cause people to engage in behavior they wouldn’t otherwise (daycare+working mother, for example).
- Inflation means that the value of your money goes down over time, which encourages people to spend more today, when their money has a larger impact. (Milton Friedman described this as high living.)
Conclusion
The idea here is simple, and fully encapsulated in the title: incentives determine outcomes. If you want to know how to get a certain outcome from others, incentivize them to want that to happen. If you want to understand why people act in seemingly irrational ways, check their incentives. If you’re confused why leaders (and especially politicians) seem to engage in destructive behavior, check their incentives.
We can bemoan these realities all we want, but they are realities. While there are some people who have a solid internal moral and ethical code, and that internal code incentivizes them to behave against their externally-incentivized interests, those people are rare. And frankly, those people are self-defeating. People should take advantage of the incentives around them. Because if they don’t, someone else will.
(If you want a literary example of that last comment, see the horse in Animal Farm.)
How do we improve the world under these conditions? Make sure the incentives align well with the overall goals of society. To me, it’s a simple formula:
- Focus on free trade, value for value, as the basis of a society. In that system, people are always incentivized to provide value to other people.
- Reduce the size of bureaucracies and large groups of all kinds. The larger an organization becomes, the farther the consequences of decisions are from those who make them.
- And since the nature of human beings will be to try and create areas where they can control the incentive systems to their own benefits, make that as difficult as possible. That comes in the form of strict limits on government power, for example.
And even if you don’t want to buy in to this conclusion, I hope the rest of the content was educational, and maybe a bit entertaining!
-
 @ 5f078e90:b2bacaa3
2025-05-28 12:00:23
@ 5f078e90:b2bacaa3
2025-05-28 12:00:23Sylvi the seahorse

In the coral haven of Azure Bay, a seahorse named Sylvi danced with the tides. Her tail curled around a swaying frond as she watched fish dart by. One dawn, a lost pearl rolled into her nook. Sylvi, curious, nudged it along the reef, meeting crabs and eels who shared tales of the deep. By dusk, she found its oyster home. The pearl gleamed thanks, and Sylvi twirled home, her heart light as foam.
Ignore this test. This was in bold originally.
(380 chars, plain text after Markdown stripping, this was in italics originally)
Originally written on habla.news (on Nostr)
-
 @ a29cfc65:484fac9c
2025-05-28 10:30:32
@ a29cfc65:484fac9c
2025-05-28 10:30:32Deutschland ist eines der wenigen Länder mit einer gesetzlich verankerten ausnahmslosen Schulbesuchspflicht. Mit den Schulschließungen in der Corona-Zeit wurde das Gesetz jedoch faktisch plötzlich außer Kraft gesetzt. Alle mussten zu Hause lernen. Als die Schulen danach wieder offen waren, wurden die Kinder mit Maskenpflicht, Tests und Impfdruck gequält. Nicht selten traten bei den Schülern Krankheiten und psychische Störungen auf. Nicht wenige Eltern suchten im Gespräch mit dem Lehrerkollegium nach Lösungen für ihre Kinder. In den meisten Fällen war das nicht möglich. Die Lehrer waren auf die neue Ideologie und die Durchsetzung der Maßnahmen eingeschworen und hatten Angst. Einige Eltern haben ihre Kinder dann in eigener Verantwortung aus der Schule genommen und zu Hause selbst unterrichtet. An manchen Orten fanden sich Gemeinschaften, wo die Kinder in Gruppen lernten. Während viele Lerngemeinschaften nicht mehr existieren, hat die Familie von Katharina den Unterricht für ihre drei Kinder in Eigenregie etabliert. Inzwischen haben sie dafür sogar „den Segen“ von Familiengericht und Jugendamt.
Katharina und Johannes leben mit ihren drei Wunschkindern Aurelius (15), Benjamin (14) und Friedrich (10) in einem Vorort von Leipzig. Die Familie wohnte früher in der Stadt. In der Corona-Zeit haben sie sich mit dem Physiotherapie- & Seminarzentrum Curasanus eine Existenz auf dem Land aufgebaut und begehen diesen Sommer ihr 20-jähriges Praxis-Jubiläum. Katharina hat ihre Arbeit als Physiotherapeutin weitgehend aufgegeben, um sich als Mama und Lernbegleiterin ihren Kindern widmen zu können. Daneben bietet sie Vorträge und Workshops an, übernimmt einen großen Teil der Praxis-Organisation und ist Manager, Rezeptionistin und Vertriebler der eigenen Firma. Wir besuchten einen ihrer Lachyoga-Kurse. Dabei erlebten wir ihr Zusammenspiel mit den drei Kindern. Anschließend stellten wir Katharina unsere Fragen zum Freilernen.
Im unmittelbaren Umfeld wird die Familie bestaunt und geachtet. Sie haben sich bewusst für das Freilernen entschieden. Die Kinder wurden ohne Test nicht mehr in die Schule gelassen. Auch andere Zwangsmaßnahmen wie die Maske wollten die Eltern den Kindern ersparen. Besonders Benjamin hatte traumatische Erlebnisse. Seine Lehrerin schmiss mit dem Schlüssel nach den Schülern und wandte andere schwarze Pädagogik an. Er ging ständig mit Bauchschmerzen ins Bett. Ein weiterer Punkt ist die Masernimpfung. Die Kinder könnten zwar zur Schule gehen, aber die Eltern werden mit rechtlichen Maßnahmen und Zwangszahlungen belegt. Da Katharina in ihrer Praxis viele Erkrankungen als Folge der Masernimpfung beobachten konnte, lehnt sie die Pflichtimpfung ab. Die Eltern haben kein Vertrauen mehr in die staatliche Schulerziehung mit all dem Zwang und den Erpressungen. Als die Familie den Entschluss gefasst hatte, die Kinder nicht mehr in die Schule zu schicken, haben sie ihre Praxis vorübergehend geschlossen, ihr Haus verkauft und sind auf Reisen gegangen. Die beiden großen Kinder wurden von der Schule abgemeldet. Nach der Rückkehr haben sie dann mit einem neuen Leben auf dem Land begonnen.
Lernen ohne Schule: Wie geht das?
„Wissen ist Macht und eine Holschuld“, sagt uns Katharina. Das ist ihr Motto und motiviert auch die Kinder. Mit dem Unterricht zu Hause macht die Familie ihre eigene Studie und zeigt, dass Lernen auch anders geht als in der Schule. Die Eltern können viel besser auf jedes einzelne Kind eingehen. Johannes arbeitete früher als Straßenbauer. Er unterstützt die Jungs vor allem in Mathematik, Geometrie und Physik sowie bei handwerklichen Fertigkeiten. Katharinas Stärken liegen in Deutsch, Sprachen und Organisation. Unter den Patienten ihrer Praxis gibt es Lehrer, die ihnen helfen. Weitere Unterstützung kommt von Freunden und Bekannten. Bei bestimmten Projekten treffen sie auf andere Freilernerkinder. „Das Netzwerk wird immer größer, es wird immer schöner und interessanter“, sagt Katharina. Man geht mit vielen anderen einen gemeinsamen Weg, verlässt dabei eingetretene Pfade und erkundet neue Themenfelder wie Mediengestaltung, freie Energie, Elektrotherapie, meditatives und Improvisations-Zeichnen. „Ich sprudele vor Ideen. Sie kommen in mein Feld, und dann mache ich was draus“, sagt Katharina. Die Jungs sind in Wurzen im Ringelnatz-Literaturkreis. Dort schreiben sie Drehbuchgeschichten und haben einen Film produziert. Sie suchen sich Projekte oder kreieren neue, wie mit dem Planetarium Eilenburg. Diese Zusammenarbeit hat sich sehr gut entwickelt. Dort lernen 4- bis 15-Jährige zusammen. Die drei Jungs spielen Klavier. Erdkunde und Geschichte erleben die Kinder auch dadurch, dass die Familie Hauptstädte oder die bosnischen Pyramiden selbst erkundet. Dabei erweist es sich als Vorteil, nicht auf die Ferienzeiten angewiesen zu sein.
Als Physiotherapeutin ist Katharina bewusst, dass man neue Lernstrategien entwickeln muss. Die Kinder lernen unterschiedlich. Jedes Kind hat seinen eigenen Charakter. Aurelius benötigt eher eine 1:1-Betreuung. Darauf kann Katharina viel individueller eingehen als die staatliche Schule. Es ist aber auch aufwendiger und anstrengender. Besonderen Wert legt sie darauf, dass rechte und linke Gehirnhälfte gleichmäßig beansprucht werden. Lernphasen werden immer wieder mit Entspannungs- oder Bewegungsphasen kombiniert. Sie weiß, dass den Kindern zuerst die Grundlagen des Lesens, Rechnens und Schreibens vermittelt werden müssen. Dann sind sie in der Lage, sich alles Weitere selbst anzueignen – Unterstützung vorausgesetzt. „Besonders das Schreiben mit der eigenen Hand ist wichtig für die Vernetzung der beiden Gehirnhälften“, sagt Katharina. Dafür nehmen sich die Eltern Zeit. Die Kinder führen Tagebuch. Außerdem halten es die Eltern für wichtig, den Kindern Werte und Tugenden wie Dankbarkeit, Verlässlichkeit, Beharrlichkeit, Aufrichtigkeit, Ehrlichkeit und die zehn Gebote zu vermitteln. Katharina und Johannes sind beide religiös begleitet aufgewachsen. Heute sehen sie die Kirche als Institution kritisch. Angebunden an die Schöpfung und im Gottvertrauen erschaffen und schöpfen sie Leben und Lebensraum aus eigener Kraft – so erklärt es uns Katharina.
Ein weiteres Thema sind die Funktionen des Körpers und wie sich die Kinder gesund erhalten können. Vieles lernen sie dabei in der Physiotherapiepraxis. Die Familie hat das Privileg, in ihrem eigenen Biorhythmus leben zu können. „Das macht sehr viel aus – wir sind alle gesund“, sagt Katharina. Der Lern- und Arbeitstag beginnt nicht vor 9 Uhr und hat eine eigene Struktur. Im Tagesablauf sind feste Verantwortlichkeiten integriert. So wechseln sich die Kinder aller drei Tage mit Tischdecken, Staubsaugen und Geschirrspüler ab. Das hilft ihnen, sich selbst zu organisieren. Das geht nicht immer reibungslos vonstatten. Wenn das Lernpensum beizeiten abgearbeitet wurde, helfen die Kinder im Haushalt oder Garten oder gehen ihrem Bewegungsdrang auf andere Weise nach. Die Eltern sind am Abend noch länger aktiv, denn die Praxis erfordert noch die eine oder andere bürokratische Pflicht. Die Familie ist sehr naturverbunden. Sie gehen viel in den Wald und in den Garten. Sie bauen selbst Gemüse und Obst an. Dabei können die Kinder zum Beispiel Erfahrungen mit Permakultur und natürlicher Düngung sammeln. Die Familie achtet auf die Ernährung, schließlich ist Katharina seit fast 25 Jahren Ernährungsberaterin. Was sie nicht selbst anbauen, wird beim Bauern des Vertrauens eingekauft. Die Jungs können selbst kochen und backen. Die Schädlichkeit von Zucker ist den Kindern schon bewusst geworden, ohne gänzlich auf Schokolade verzichten zu müssen. Medikamente gibt es im Haushalt nicht. Sie kennen sich sehr gut mit den Heilmitteln aus der Natur aus und können so ihre Selbstheilungskräfte aktivieren. Sie haben keinen Hausarzt. Natürlich hat keines der Kinder ein Handy. Bisher haben sie noch kein Verlangen danach. Die Eltern halten es für wichtig, dass die Kinder erst sicher bei Selbstorganisation und Tagesstruktur sind, bevor sie ein Handy bekommen. Katharina weist darauf hin, dass beispielsweise WhatsApp erst ab 16 Jahren zugelassen ist, und fragt sich, ob das andere Eltern wissen.
Gesetze auf Augenhöhe auslegen
Den Behörden blieben die Freilerner nicht verborgen. Sie wurden aktiv und schalteten das Familiengericht ein. Die Familie hatte keinen Anwalt und keine Rechtsschutzversicherung. Katharina erzählt uns, dass sie schließlich auf „Hilfe von oben“ gehofft habe. Irgendwer hat sie anscheinend erhört, denn sie bekamen „einen Engel“ als Verfahrensbeistand. Die Behörden waren sehr zugänglich. In den Gesprächen gab man zu, mit der Schulsituation ebenfalls nicht zufrieden zu sein. „Wir wollen so wie ihr, dass sich etwas verändert. Wir sind an Eurer Seite.“ Die Gespräche mit dem Jugendamt und der Richterin vom Familiengericht Grimma waren immer auf Augenhöhe. Schließlich legte man der Familie keine Steine in den Weg. Damit kann Katharina ihr Konzept nach außen leben und andere inspirieren. Ihre Schlussfolgerung: Eltern müssen sich ihrer Stärken bewusst werden und aus ihrer Angst herauskommen. Das Konzept muss aber zur Familie passen, denn jede Familie ist anders.
Die Basis für freies Lernen ist das Vertrauen der Eltern in ihre Kinder. Denn Kinder sind von Natur aus wissbegierig und wollen lernen. Katharina hat viel von Bertrand Stern und von Riccardo Leppe gelernt. Beiden wurde von ihren Eltern das Lernen ohne Schulbesuch ermöglicht. Mit Bertrand Stern hat Katharina Kontakt. Er wird im November am Buß- und Bettag eine kleine Fortbildung im Therapie- und Seminarzentrum geben. Für den Vorabend ist ein Vortrag geplant. Katharina zitiert Riccardo Leppe: „Es ändert sich nur was, wenn man es selbst tut.“ Er sei sich sicher, dass der Fortschritt beim Freilernen inzwischen so weit ist, dass „die Paste nicht wieder zurück in die Tube geht“.
Der Übergang zur Berufsausbildung
Die ersten Freilernerkinder kommen jetzt in das Alter, in dem sie eine Berufsausbildung beginnen können. Aurelius und Benjamin, die beiden „Großen“, machen seit Anfang des Jahres schon erste Praktika bei ortsansässigen Handwerksbetrieben. Beide Seiten sind sehr zufrieden. Durch die Praktika, die länger dauern als im schulischen Lehrplan vorgesehen, können sich die Kinder ausprobieren. Katharina findet es interessant miterleben zu dürfen, wie auf ihre Kinder reagiert wird. Bringen sie etwas mit, das die anderen nicht haben? Denken sie anders mit? Benjamin bekam schon ein Angebot, in einem Metallbau-Betrieb stundenweise mitzuarbeiten. In den Betrieben weiß man, dass die Abschlüsse der staatlichen Schulen größtenteils das Papier nicht wert sind, auf dem sie stehen. Viele verlassen die Schule und können kaum lesen und schreiben, von Selbstorganisation ganz zu schweigen. Ein Freilerner kann eine staatliche Externen-Prüfung ablegen, um einen Haupt- oder Realschulabschluss zu erwerben. Katharina: „Für eine Ausbildung bei einem privaten Unternehmer braucht man das nicht, allein der Unternehmer entscheidet über die Aufnahme des Auszubildenden“. Außerdem stehen den jungen Leuten Privatschulen oder der zweite Bildungsweg zur Verfügung. Wenn man einen praktischen Beruf ergreift, ist es immer noch möglich, sich bis zur Hochschulreife weiterzubilden. Nach mehrjährigen Tätigkeiten kann man bei den Kammern von Industrie, Handel und Handwerk (IHK und HWK) eine Abschlussprüfung ablegen, mit der man zum Studium zugelassen werden kann. Oder man geht gleich den Weg in die Selbstständigkeit.
Frei lernen weitergedacht
Während der Coronazeit haben sich in Sachsen und speziell um Leipzig herum kleine Freilernergruppen gefunden. Die Gruppen werden aktuell zusammengeführt, um zum Beispiel gemeinsam den Mathematikunterricht zu gestalten. Besonders um Dresden herum ist die Szene noch stärker ausgeprägt. Außerdem gibt es seit mehr als 20 Jahren den Bundesverband Natürlich Lernen (BVNL). Er bietet Beratung und zentrale Veranstaltungen an.
Der Wunsch nach dem freien Lernen ohne Schulzwang ist groß. Doch die meisten Eltern wollen ihre Kinder dafür irgendwo abgeben und nicht selbst unterrichten. Katharinas größter Wunsch ist es, drei bis fünf Elternpaare zu finden, die sich in die Betreuung und Unterrichtung ihrer Kinder teilen. Das größte Hindernis dafür sieht sie in den Eltern selbst. Durch ungelöste transgenerative Konflikte und unverarbeitete Familientraumata kommen sie noch nicht in ihre eigene Kraft für ein selbstbestimmtes Leben. Viele wagen es noch nicht, ihre Erwerbstätigkeit zugunsten der Kinder einzuschränken. Katharina sieht es als große Aufgabe für sich und ihre Familie, mit dem Freilernen das Gemeinschaftsbewusstsein und gute Konfliktlösungsstrategien zu entwickeln. Sie denkt dabei bereits an ihre Enkel. Aber sie weiß auch, dass die Eltern ein sehr hohes Maß an Eigeninitiative, Motivation und Selbstdisziplin aufbringen müssen. Sie würde Eltern, die sich das noch nicht zutrauen, als Traumabegleiterin zur Verfügung stehen, für einen angemessenen Energieausgleich. Diese gegenseitige Unterstützung käme Kindern und Eltern zugute. Ebenso hält sie die Idee der Mehrgenerationenerziehung für wichtig. Dabei profitieren nicht nur die Kinder. Die Erfahrungen der älteren Menschen gehen nicht verloren, sondern werden an die jüngeren Generationen weitergegeben und machen sie resilienter. Das hilft den Eltern, ihrer Erwerbsarbeit nachzugehen und Familientraumata zu bewältigen.
Katharina ist eine starke Frau und sprüht nur so vor Energie. Selbst als wir nach 21 Uhr das Therapiezentrum verlassen, sind ihr die Anstrengungen des Tages nicht anzumerken. Sie wird nicht müde beim Sprechen. Für Fragen zum Thema Freilernen kann man sich an sie wenden.
Der Text wurde zuerst am 27.05.2025 im Blog „Freie Akademie für Medien und Journalismus“ veröffentlicht (https://www.freie-medienakademie.de/medien-plus/lernen-neu-gemacht)
Bildquelle: Salah Darwish, unsplash.com
-
 @ 005bc4de:ef11e1a2
2025-05-28 09:05:10
@ 005bc4de:ef11e1a2
2025-05-28 09:05:10
BIP-2,100,000,000,000,000,000
So, you're telling me...
- 21 million bitcoins is out, and...
- 2.1 quadrillion sats is in, except that...
- sats are out, so...
- 2.1 quadrillion bitcoins is in, except that...
- there are actually millisats, but...
- millisats are out, so...
- millibitcoins are in, so now...
- there are 2.1 quintillion millibitcoins, except that...
- millibitcoins are the basic base unit of bitcoin, so...
- millibitcoins are out, and now...
- 2.1 quintillion bitcoins are in
-
 @ 58537364:705b4b85
2025-05-28 08:25:55
@ 58537364:705b4b85
2025-05-28 08:25:55ถ้าอยากแล้วไม่หลง มันก็อยากด้วยปัญญา ความอยากอย่างนี้ท่านเรียกว่า เป็นบารมีของตน แต่ไม่ใช่ทุกคนนะที่มีปัญญา
บางคนไม่อยากจะให้มันอยาก เพราะเข้าใจว่า การมาปฏิบัติก็เพื่อระงับความอยาก ความจริงน่ะ ถ้าหากว่าไม่มีความอยาก ก็ไม่มีข้อปฏิบัติ ไม่รู้ว่าจะทำอะไร ลองพิจารณาดูก็ได้
ทุกคน แม้องค์พระพุทธเจ้าของเราก็ตาม ที่ท่านออกมาปฏิบัติ ก็เพื่อจะให้บรรเทากิเลสทั้งหลายนั้น
แต่ว่ามันต้องอยากทำ อยากปฏิบัติ อยากให้มันสงบ และก็ไม่อยากให้มันวุ่นวาย ทั้งสองอย่างนี้ มันเป็นอุปสรรคทั้งนั้น ถ้าเราไม่มีปัญญา ไม่มีความฉลาดในการกระทำอย่างนั้น เพราะว่ามันปนกันอยู่ อยากทั้งสองอย่างนี้มันมีราคาเท่า ๆ กัน
อยากจะพ้นทุกข์มันเป็นกิเลส สำหรับคนไม่มีปัญญา อยากด้วยความโง่ ไม่อยากมันก็เป็นกิเลส เพราะไม่อยากอันนั้นมันประกอบด้วยความโง่เหมือนกัน คือทั้งอยาก ไม่อยาก ปัญญาก็ไม่มี ทั้งสองอย่างนี้ มันเป็นกามสุขัลลิกานุโยโค กับอัตตกิลมถานุโยโค ซึ่งพระพุทธองค์ของเรา ขณะที่พระองค์กำลังทรงปฏิบัติอยู่นั้น ท่านก็หลงใหลในอย่างนี้ ไม่รู้ว่าจะทำอย่างไร ท่านหาอุบายหลายประการ กว่าจะพบของสองสิ่งนี้
ทุกวันนี้เราทั้งหลายก็เหมือนกัน ทุกสิ่งทั้งสองอย่างนี้มันกวนอยู่ เราจึงเข้าสู่ทางไม่ได้ก็เพราะอันนี้ ความเป็นจริงนี้ทุกคนที่มาปฏิบัติ ก็เป็นปุถุชนมาทั้งนั้น ปุถุชนก็เต็มไปด้วยความอยาก ความอยากที่ไม่มีปัญญา อยากด้วยความหลง ไม่อยากมันก็มีโทษเหมือนกัน “ไม่อยาก” มันก็เป็นตัณหา “อยาก” มันก็เป็นตัณหาอีกเหมือนกัน
ทีนี้ นักปฏิบัติยังไม่รู้เรื่องว่า จะเอายังไงกัน เดินไปข้างหน้าก็ไม่ถูก เดินกลับไปข้างหลังก็ไม่ถูก จะหยุดก็หยุดไม่ได้เพราะมันยังอยากอยู่ มันยังหลงอยู่ มีแต่ความอยาก แต่ปัญญาไม่มี มันอยากด้วยความหลง มันก็เป็นตัณหา ถึงแม้ไม่อยาก มันก็เป็นความหลง มันก็เป็นตัณหาเหมือนกันเพราะอะไร? เพราะมันขาดปัญญา
ความเป็นจริงนั้น ธรรมะมันอยู่ตรงนั้นแหละ ตรงความอยากกับความไม่อยากนั่นแหละ แต่เราไม่มีปัญญา ก็พยายามไม่ให้อยากบ้าง เดี๋ยวก็อยากบ้าง อยากให้เป็นอย่างนั้น ไม่อยากให้เป็นอย่างนี้ ความจริงทั้งสองอย่างนี้ หรือทั้งคู่นี้มันตัวเดียวกันทั้งนั้น ไม่ใช่คนละตัว แต่เราไม่รู้เรื่องของมัน
พระพุทธเจ้าของเรา และสาวกทั้งหลายของพระองค์นั้นท่านก็อยากเหมือนกัน แต่ “อยาก” ของท่านนั้น เป็นเพียงอาการของจิตเฉย ๆ หรือ “ไม่อยาก” ของท่าน ก็เป็นเพียงอาการของจิตเฉย ๆ อีกเหมือนกัน มันวูบเดียวเท่านั้น ก็หายไปแล้ว
ดังนั้น ความอยากหรือไม่อยากนี้ มันมีอยู่ตลอดเวลาแต่สำหรับผู้มีปัญญานั้น “อยาก” ก็ไม่มีอุปาทาน “ไม่อยาก” ก็ไม่มีอุปาทาน เป็น “สักแต่ว่า” อยากหรือไม่อยากเท่านั้น ถ้าพูดตามความจริงแล้ว มันก็เป็นแต่ "อาการของจิต" อาการของจิตมันเป็นของมันอย่างนั้นเอง ถ้าเรามาตะครุบมันอยู่ใกล้ ๆ นี่มันก็เห็นชัด
ดังนั้นจึงว่า การพิจารณานั้น ไม่ใช่รู้ไปที่อื่น มันรู้ตรงนี้แหละ เหมือนชาวประมงที่ออกไปทอดแหนั่นแหละ ทอดแหออกไปถูกปลาตัวใหญ่ เจ้าของผู้ทอดแหจะคิดอย่างไร? ก็กลัว กลัวปลาจะออกจากแหไปเสีย เมื่อเป็นเช่นนั้น ใจมันก็ดิ้นรนขึ้นระวังมาก บังคับมาก ตะครุบไปตะครุบมาอยู่นั่นแหละ ประเดี๋ยวปลามันก็ออกจากแหไปเสีย เพราะไปตะครุบมันแรงเกินไป
อย่างนั้นโบราณท่านพูดถึงเรื่องอันนี้ ท่านว่าค่อย ๆ ทำมัน แต่อย่าไปห่างจากมัน นี่คือปฏิปทาของเรา ค่อย ๆ คลำมันไปเรื่อย ๆ อย่างนั้นแหละ
อย่าปล่อยมัน หรือไม่อยากรู้มัน ต้องรู้ ต้องรู้เรื่องของมัน พยายามทำมันไปเรื่อย ๆ ให้เป็นปฏิปทา ขี้เกียจเราก็ทำไม่ขี้เกียจเราก็ทำ เรียกว่าการทำการปฏิบัติ ต้องทำไปเรื่อยๆอย่างนี้
ถ้าหากว่าเราขยัน ขยันเพราะความเชื่อ มันมีศรัทธาแต่ปัญญาไม่มี ถ้าเป็นอย่างนี้ ขยันไป ๆ แล้วมันก็ไม่เกิดผลอะไรขึ้นมากมาย ขยันไปนาน ๆ เข้า แต่มันไม่ถูกทาง มันก็ไม่สงบระงับ ทีนี้ก็จะเกิดความคิดว่า เรานี้บุญน้อยหรือวาสนาน้อย หรือคิดไปว่ามนุษย์ในโลกนี้คงทำไม่ได้หรอก แล้วก็เลยหยุดเลิกทำเลิกปฏิบัติ
ถ้าเกิดความคิดอย่างนี้เมื่อใด ขอให้ระวังให้มาก ให้มีขันติ ความอดทน ให้ทำไปเรื่อย ๆ เหมือนกับเราจับปลาตัวใหญ่ ก็ให้ค่อย ๆ คลำมันไปเรื่อย ๆ ปลามันก็จะไม่ดิ้นแรงค่อย ๆทำไปเรื่อย ๆ ไม่หยุด ไม่ช้าปลาก็จะหมดกำลัง มันก็จับง่าย จับให้ถนัดมือเลย ถ้าเรารีบจนเกินไป ปลามันก็จะหนีดิ้นออกจากแหเท่านั้น
ดังนั้น การปฏิบัตินี้ ถ้าเราพิจารณาตามพื้นเหตุของเรา เช่นว่า เราไม่มีความรู้ในปริยัติ ไม่มีความรู้ในอะไรอื่น ที่จะให้การปฏิบัติมันเกิดผลขึ้น ก็ดูความรู้ที่เป็นพื้นเพเดิมของเรานั่นแหละอันนั้นก็คือ “ธรรมชาติของจิต” นี่เอง มันมีของมันอยู่แล้ว เราจะไปเรียนรู้มัน มันก็มีอยู่ หรือเราจะไม่ไปเรียนรู้มัน มันก็มีอยู่
อย่างที่ท่านพูดว่า พระพุทธเจ้าจะบังเกิดขึ้นก็ตาม หรือไม่บังเกิดขึ้นก็ตาม ธรรมะก็คงมีอยู่อย่างนั้น มันเป็นของมันอยู่อย่างนั้น ไม่พลิกแพลงไปไหน มันเป็นสัจจธรรม
เราไม่เข้าใจสัจจธรรม ก็ไม่รู้ว่าสัจจธรรมเป็นอย่างไร นี้เรียกว่า การพิจารณาในความรู้ของผู้ปฏิบัติที่ไม่มีพื้นปริยัติ
ขอให้ดูจิต พยายามอ่านจิตของเจ้าของ พยายามพูดกับจิตของเจ้าของ มันจึงจะรู้เรื่องของจิต ค่อย ๆ ทำไป ถ้ายังไม่ถึงที่ของมัน มันก็ไปอยู่อย่างนั้น
ครูบาอาจารย์บางท่านบอกว่า ทำไปเรื่อย ๆ อย่าหยุด บางทีเรามาคิด “เออ ทำไปเรื่อย ๆ ถ้าไม่รู้เรื่องของมัน ถ้าทำไม่ถูกที่มัน มันจะรู้อะไร” อย่างนี้เป็นต้น ก็ต้องไปเรื่อย ๆ ก่อน แล้วมันก็จะเกิดความรู้สึกนึกคิดขึ้นในสิ่งที่เราพากเพียรทำนั้น
มันเหมือนกันกับบุรุษที่ไปสีไฟ ได้ฟังท่านบอกว่า เอาไม้ไผ่สองอันมาสีกันเข้าไปเถอะ แล้วจะมีไฟเกิดขึ้น บุรุษนั้นก็จับไม้ไผ่เข้าสองอัน สีกันเข้า แต่ใจร้อน สีไปได้หน่อย ก็อยากให้มันเป็นไฟ ใจก็เร่งอยู่เรื่อย ให้เป็นไฟเร็วๆ แต่ไฟก็ไม่เกิดสักที บุรุษนั้นก็เกิดความขี้เกียจ แล้วก็หยุดพัก แล้วจึงลองสีอีกนิด แล้วก็หยุดพัก ความร้อนที่พอมีอยู่บ้าง ก็หายไปล่ะซิ เพราะความร้อนมันไม่ติดต่อกัน
ถ้าทำไปเรื่อยๆอย่างนี้ เหนื่อยก็หยุด มีแต่เหนื่อยอย่างเดียวก็พอได้ แต่มีขี้เกียจปนเข้าด้วย เลยไปกันใหญ่ แล้วบุรุษนั้นก็หาว่าไฟไม่มี ไม่เอาไฟ ก็ทิ้ง เลิก ไม่สีอีก แล้วก็ไปเที่ยวประกาศว่า ไฟไม่มี ทำอย่างนี้ไม่ได้ ไม่มีไฟหรอก เขาได้ลองทำแล้ว
ก็จริงเหมือนกันที่ได้ทำแล้ว แต่ทำยังไม่ถึงจุดของมันคือความร้อนยังไม่สมดุลกัน ไฟมันก็เกิดขึ้นไม่ได้ ทั้งที่ความจริงไฟมันก็มีอยู่ อย่างนี้ก็เกิดความท้อแท้ขึ้นในใจของผู้ปฏิบัตินั้น ก็ละอันนี้ไปทำอันโน้นเรื่อยไป อันนี้ฉันใดก็ฉันนั้น
การปฏิบัตินั้น ปฏิบัติทางกายทางใจทั้งสองอย่าง มันต้องพร้อมกัน เพราะอะไร? เพราะพื้นเพมันเป็นคนมีกิเลสทั้งนั้น พระพุทธเจ้าก่อนที่จะเป็นพระพุทธเจ้า ท่านก็มีกิเลสแต่ท่านมีปัญญามากหลาย พระอรหันต์ก็เหมือนกัน เมื่อยังเป็นปุถุชนอยู่ ก็เหมือนกับเรา
เมื่อความอยากเกิดขึ้นมา เราก็ไม่รู้จัก เมื่อความไม่อยากเกิดขึ้นมา เราก็ไม่รู้จัก บางทีก็ร้อนใจ บางทีก็ดีใจ ถ้าใจเราไม่อยาก ก็ดีใจแบบหนึ่ง และวุ่นวายอีกแบบหนึ่ง ถ้าใจเราอยาก มันก็วุ่นวายอย่างหนึ่ง และดีใจอย่างหนึ่ง มันประสมประเสกันอยู่อย่างนี้
อันนี้คือปฏิปทาของผู้ปฏิบัติเรา
[อ่านใจธรรมชาติ] หลวงปู่ชา สุภัทโท หนังสือ หมวด: โพธิญาณ
-
 @ 3f770d65:7a745b24
2025-01-12 21:03:36
@ 3f770d65:7a745b24
2025-01-12 21:03:36I’ve been using Notedeck for several months, starting with its extremely early and experimental alpha versions, all the way to its current, more stable alpha releases. The journey has been fascinating, as I’ve had the privilege of watching it evolve from a concept into a functional and promising tool.
In its earliest stages, Notedeck was raw—offering glimpses of its potential but still far from practical for daily use. Even then, the vision behind it was clear: a platform designed to redefine how we interact with Nostr by offering flexibility and power for all users.
I'm very bullish on Notedeck. Why? Because Will Casarin is making it! Duh! 😂
Seriously though, if we’re reimagining the web and rebuilding portions of the Internet, it’s important to recognize the potential of Notedeck. If Nostr is reimagining the web, then Notedeck is reimagining the Nostr client.
Notedeck isn’t just another Nostr app—it’s more a Nostr browser that functions more like an operating system with micro-apps. How cool is that?
Much like how Google's Chrome evolved from being a web browser with a task manager into ChromeOS, a full blown operating system, Notedeck aims to transform how we interact with the Nostr. It goes beyond individual apps, offering a foundation for a fully integrated ecosystem built around Nostr.
As a Nostr evangelist, I love to scream INTEROPERABILITY and tout every application's integrations. Well, Notedeck has the potential to be one of the best platforms to showcase these integrations in entirely new and exciting ways.
Do you want an Olas feed of images? Add the media column.
Do you want a feed of live video events? Add the zap.stream column.
Do you want Nostr Nests or audio chats? Add that column to your Notedeck.
Git? Email? Books? Chat and DMs? It's all possible.
Not everyone wants a super app though, and that’s okay. As with most things in the Nostr ecosystem, flexibility is key. Notedeck gives users the freedom to choose how they engage with it—whether it’s simply following hashtags or managing straightforward feeds. You'll be able to tailor Notedeck to fit your needs, using it as extensively or minimally as you prefer.
Notedeck is designed with a local-first approach, utilizing Nostr content stored directly on your device via the local nostrdb. This will enable a plethora of advanced tools such as search and filtering, the creation of custom feeds, and the ability to develop personalized algorithms across multiple Notedeck micro-applications—all with unparalleled flexibility.
Notedeck also supports multicast. Let's geek out for a second. Multicast is a method of communication where data is sent from one source to multiple destinations simultaneously, but only to devices that wish to receive the data. Unlike broadcast, which sends data to all devices on a network, multicast targets specific receivers, reducing network traffic. This is commonly used for efficient data distribution in scenarios like streaming, conferencing, or large-scale data synchronization between devices.
In a local first world where each device holds local copies of your nostr nodes, and each device transparently syncs with each other on the local network, each node becomes a backup. Your data becomes antifragile automatically. When a node goes down it can resync and recover from other nodes. Even if not all nodes have a complete collection, negentropy can pull down only what is needed from each device. All this can be done without internet.
-Will Casarin
In the context of Notedeck, multicast would allow multiple devices to sync their Nostr nodes with each other over a local network without needing an internet connection. Wild.
Notedeck aims to offer full customization too, including the ability to design and share custom skins, much like Winamp. Users will also be able to create personalized columns and, in the future, share their setups with others. This opens the door for power users to craft tailored Nostr experiences, leveraging their expertise in the protocol and applications. By sharing these configurations as "Starter Decks," they can simplify onboarding and showcase the best of Nostr’s ecosystem.
Nostr’s “Other Stuff” can often be difficult to discover, use, or understand. Many users doesn't understand or know how to use web browser extensions to login to applications. Let's not even get started with nsecbunkers. Notedeck will address this challenge by providing a native experience that brings these lesser-known applications, tools, and content into a user-friendly and accessible interface, making exploration seamless. However, that doesn't mean Notedeck should disregard power users that want to use nsecbunkers though - hint hint.
For anyone interested in watching Nostr be developed live, right before your very eyes, Notedeck’s progress serves as a reminder of what’s possible when innovation meets dedication. The current alpha is already demonstrating its ability to handle complex use cases, and I’m excited to see how it continues to grow as it moves toward a full release later this year.
-
 @ 21810ca8:f2e8341e
2025-05-28 08:10:53
@ 21810ca8:f2e8341e
2025-05-28 08:10:53Ich bin neu bei Nostr und versuche mich hier rein zu fuchsen. Kann das einer sehen? Und dann habe ich noch viele Fragen
Gibt es gute Marktplätze wie ebay oder ebay kleinanzeigen wo man stink normale dinge und kram von zuhause gegen sat verkaufen kann.
-
 @ 1bda7e1f:bb97c4d9
2025-01-02 05:19:08
@ 1bda7e1f:bb97c4d9
2025-01-02 05:19:08Tldr
- Nostr is an open and interoperable protocol
- You can integrate it with workflow automation tools to augment your experience
- n8n is a great low/no-code workflow automation tool which you can host yourself
- Nostrobots allows you to integrate Nostr into n8n
- In this blog I create some workflow automations for Nostr
- A simple form to delegate posting notes
- Push notifications for mentions on multiple accounts
- Push notifications for your favourite accounts when they post a note
- All workflows are provided as open source with MIT license for you to use
Inter-op All The Things
Nostr is a new open social protocol for the internet. This open nature exciting because of the opportunities for interoperability with other technologies. In Using NFC Cards with Nostr I explored the
nostr:URI to launch Nostr clients from a card tap.The interoperability of Nostr doesn't stop there. The internet has many super-powers, and Nostr is open to all of them. Simply, there's no one to stop it. There is no one in charge, there are no permissioned APIs, and there are no risks of being de-platformed. If you can imagine technologies that would work well with Nostr, then any and all of them can ride on or alongside Nostr rails.
My mental model for why this is special is Google Wave ~2010. Google Wave was to be the next big platform. Lars was running it and had a big track record from Maps. I was excited for it. Then, Google pulled the plug. And, immediately all the time and capital invested in understanding and building on the platform was wasted.
This cannot happen to Nostr, as there is no one to pull the plug, and maybe even no plug to pull.
So long as users demand Nostr, Nostr will exist, and that is a pretty strong guarantee. It makes it worthwhile to invest in bringing Nostr into our other applications.
All we need are simple ways to plug things together.
Nostr and Workflow Automation
Workflow automation is about helping people to streamline their work. As a user, the most common way I achieve this is by connecting disparate systems together. By setting up one system to trigger another or to move data between systems, I can solve for many different problems and become way more effective.
n8n for workflow automation
Many workflow automation tools exist. My favourite is n8n. n8n is a low/no-code workflow automation platform which allows you to build all kinds of workflows. You can use it for free, you can self-host it, it has a user-friendly UI and useful API. Vs Zapier it can be far more elaborate. Vs Make.com I find it to be more intuitive in how it abstracts away the right parts of the code, but still allows you to code when you need to.
Most importantly you can plug anything into n8n: You have built-in nodes for specific applications. HTTP nodes for any other API-based service. And community nodes built by individual community members for any other purpose you can imagine.
Eating my own dogfood
It's very clear to me that there is a big design space here just demanding to be explored. If you could integrate Nostr with anything, what would you do?
In my view the best way for anyone to start anything is by solving their own problem first (aka "scratching your own itch" and "eating your own dogfood"). As I get deeper into Nostr I find myself controlling multiple Npubs – to date I have a personal Npub, a brand Npub for a community I am helping, an AI assistant Npub, and various testing Npubs. I need ways to delegate access to those Npubs without handing over the keys, ways to know if they're mentioned, and ways to know if they're posting.
I can build workflows with n8n to solve these issues for myself to start with, and keep expanding from there as new needs come up.
Running n8n with Nostrobots
I am mostly non-technical with a very helpful AI. To set up n8n to work with Nostr and operate these workflows should be possible for anyone with basic technology skills.
- I have a cheap VPS which currently runs my HAVEN Nostr Relay and Albyhub Lightning Node in Docker containers,
- My objective was to set up n8n to run alongside these in a separate Docker container on the same server, install the required nodes, and then build and host my workflows.
Installing n8n
Self-hosting n8n could not be easier. I followed n8n's Docker-Compose installation docs–
- Install Docker and Docker-Compose if you haven't already,
- Create your
docker-compose.ymland.envfiles from the docs, - Create your data folder
sudo docker volume create n8n_data, - Start your container with
sudo docker compose up -d, - Your n8n instance should be online at port
5678.
n8n is free to self-host but does require a license. Enter your credentials into n8n to get your free license key. You should now have access to the Workflow dashboard and can create and host any kind of workflows from there.
Installing Nostrobots
To integrate n8n nicely with Nostr, I used the Nostrobots community node by Ocknamo.
In n8n parlance a "node" enables certain functionality as a step in a workflow e.g. a "set" node sets a variable, a "send email" node sends an email. n8n comes with all kinds of "official" nodes installed by default, and Nostr is not amongst them. However, n8n also comes with a framework for community members to create their own "community" nodes, which is where Nostrobots comes in.
You can only use a community node in a self-hosted n8n instance (which is what you have if you are running in Docker on your own server, but this limitation does prevent you from using n8n's own hosted alternative).
To install a community node, see n8n community node docs. From your workflow dashboard–
- Click the "..." in the bottom left corner beside your username, and click "settings",
- Cilck "community nodes" left sidebar,
- Click "Install",
- Enter the "npm Package Name" which is
n8n-nodes-nostrobots, - Accept the risks and click "Install",
- Nostrobots is now added to your n8n instance.
Using Nostrobots
Nostrobots gives you nodes to help you build Nostr-integrated workflows–
- Nostr Write – for posting Notes to the Nostr network,
- Nostr Read – for reading Notes from the Nostr network, and
- Nostr Utils – for performing certain conversions you may need (e.g. from bech32 to hex).
Nostrobots has good documentation on each node which focuses on simple use cases.
Each node has a "convenience mode" by default. For example, the "Read" Node by default will fetch Kind 1 notes by a simple filter, in Nostrobots parlance a "Strategy". For example, with Strategy set to "Mention" the node will accept a pubkey and fetch all Kind 1 notes that Mention the pubkey within a time period. This is very good for quick use.
What wasn't clear to me initially (until Ocknamo helped me out) is that advanced use cases are also possible.
Each node also has an advanced mode. For example, the "Read" Node can have "Strategy" set to "RawFilter(advanced)". Now the node will accept json (anything you like that complies with NIP-01). You can use this to query Notes (Kind 1) as above, and also Profiles (Kind 0), Follow Lists (Kind 3), Reactions (Kind 7), Zaps (Kind 9734/9735), and anything else you can think of.
Creating and adding workflows
With n8n and Nostrobots installed, you can now create or add any kind of Nostr Workflow Automation.
- Click "Add workflow" to go to the workflow builder screen,
- If you would like to build your own workflow, you can start with adding any node. Click "+" and see what is available. Type "Nostr" to explore the Nostrobots nodes you have added,
- If you would like to add workflows that someone else has built, click "..." in the top right. Then click "import from URL" and paste in the URL of any workflow you would like to use (including the ones I share later in this article).
Nostr Workflow Automations
It's time to build some things!
A simple form to post a note to Nostr
I started very simply. I needed to delegate the ability to post to Npubs that I own in order that a (future) team can test things for me. I don't want to worry about managing or training those people on how to use keys, and I want to revoke access easily.
I needed a basic form with credentials that posted a Note.
For this I can use a very simple workflow–
- A n8n Form node – Creates a form for users to enter the note they wish to post. Allows for the form to be protected by a username and password. This node is the workflow "trigger" so that the workflow runs each time the form is submitted.
- A Set node – Allows me to set some variables, in this case I set the relays that I intend to use. I typically add a Set node immediately following the trigger node, and put all the variables I need in this. It helps to make the workflows easier to update and maintain.
- A Nostr Write node (from Nostrobots) – Writes a Kind-1 note to the Nostr network. It accepts Nostr credentials, the output of the Form node, and the relays from the Set node, and posts the Note to those relays.
Once the workflow is built, you can test it with the testing form URL, and set it to "Active" to use the production form URL. That's it. You can now give posting access to anyone for any Npub. To revoke access, simply change the credentials or set to workflow to "Inactive".
It may also be the world's simplest Nostr client.
You can find the Nostr Form to Post a Note workflow here.
Push notifications on mentions and new notes
One of the things Nostr is not very good at is push notifications. Furthermore I have some unique itches to scratch. I want–
- To make sure I never miss a note addressed to any of my Npubs – For this I want a push notification any time any Nostr user mentions any of my Npubs,
- To make sure I always see all notes from key accounts – For this I need a push notification any time any of my Npubs post any Notes to the network,
- To get these notifications on all of my devices – Not just my phone where my Nostr regular client lives, but also on each of my laptops to suit wherever I am working that day.
I needed to build a Nostr push notifications solution.
To build this workflow I had to string a few ideas together–
- Triggering the node on a schedule – Nostrobots does not include a trigger node. As every workflow starts with a trigger we needed a different method. I elected to run the workflow on a schedule of every 10-minutes. Frequent enough to see Notes while they are hot, but infrequent enough to not burden public relays or get rate-limited,
- Storing a list of Npubs in a Nostr list – I needed a way to store the list of Npubs that trigger my notifications. I initially used an array defined in the workflow, this worked fine. Then I decided to try Nostr lists (NIP-51, kind 30000). By defining my list of Npubs as a list published to Nostr I can control my list from within a Nostr client (e.g. Listr.lol or Nostrudel.ninja). Not only does this "just work", but because it's based on Nostr lists automagically Amethyst client allows me to browse that list as a Feed, and everyone I add gets notified in their Mentions,
- Using specific relays – I needed to query the right relays, including my own HAVEN relay inbox for notes addressed to me, and wss://purplepag.es for Nostr profile metadata,
- Querying Nostr events (with Nostrobots) – I needed to make use of many different Nostr queries and use quite a wide range of what Nostrobots can do–
- I read the EventID of my Kind 30000 list, to return the desired pubkeys,
- For notifications on mentions, I read all Kind 1 notes that mention that pubkey,
- For notifications on new notes, I read all Kind 1 notes published by that pubkey,
- Where there are notes, I read the Kind 0 profile metadata event of that pubkey to get the displayName of the relevant Npub,
- I transform the EventID into a Nevent to help clients find it.
- Using the Nostr URI – As I did with my NFC card article, I created a link with the
nostr:URI prefix so that my phone's native client opens the link by default, - Push notifications solution – I needed a push notifications solution. I found many with n8n integrations and chose to go with Pushover which supports all my devices, has a free trial, and is unfairly cheap with a $5-per-device perpetual license.
Once the workflow was built, lists published, and Pushover installed on my phone, I was fully set up with push notifications on Nostr. I have used these workflows for several weeks now and made various tweaks as I went. They are feeling robust and I'd welcome you to give them a go.
You can find the Nostr Push Notification If Mentioned here and If Posts a Note here.
In speaking with other Nostr users while I was building this, there are all kind of other needs for push notifications too – like on replies to a certain bookmarked note, or when a followed Npub starts streaming on zap.stream. These are all possible.
Use my workflows
I have open sourced all my workflows at my Github with MIT license and tried to write complete docs, so that you can import them into your n8n and configure them for your own use.
To import any of my workflows–
- Click on the workflow of your choice, e.g. "Nostr_Push_Notify_If_Mentioned.json",
- Click on the "raw" button to view the raw JSON, ex any Github page layout,
- Copy that URL,
- Enter that URL in the "import from URL" dialog mentioned above.
To configure them–
- Prerequisites, credentials, and variables are all stated,
- In general any variables required are entered into a Set Node that follows the trigger node,
- Pushover has some extra setup but is very straightforward and documented in the workflow.
What next?
Over my first four blogs I explored creating a good Nostr setup with Vanity Npub, Lightning Payments, Nostr Addresses at Your Domain, and Personal Nostr Relay.
Then in my latest two blogs I explored different types of interoperability with NFC cards and now n8n Workflow Automation.
Thinking ahead n8n can power any kind of interoperability between Nostr and any other legacy technology solution. On my mind as I write this:
- Further enhancements to posting and delegating solutions and forms (enhanced UI or different note kinds),
- Automated or scheduled posting (such as auto-liking everything Lyn Alden posts),
- Further enhancements to push notifications, on new and different types of events (such as notifying me when I get a new follower, on replies to certain posts, or when a user starts streaming),
- All kinds of bridges, such as bridging notes to and from Telegram, Slack, or Campfire. Or bridging RSS or other event feeds to Nostr,
- All kinds of other automation (such as BlackCoffee controlling a coffee machine),
- All kinds of AI Assistants and Agents,
In fact I have already released an open source workflow for an AI Assistant, and will share more about that in my next blog.
Please be sure to let me know if you think there's another Nostr topic you'd like to see me tackle.
GM Nostr.
-
 @ 3770c235:16042bcc
2025-05-28 05:54:01
@ 3770c235:16042bcc
2025-05-28 05:54:01** Introduction: The Neon Pulse of Las Vegas
**It’s 2:30 AM on a Tuesday. The Strip hums with laughter, clinking glasses, and the occasional Elvis impersonator. A group of friends stumbles out of a nightclub, squinting under the glow of a Las Vegas billboard that screams, “Hungry? $5 Pancakes → 1 Block Right!” Ten minutes later, they’re drowning their late-night cravings in syrup.This isn’t luck—it’s Las Vegas billboards doing what they do best: working while the rest of the world sleeps. In a city where the party never stops, these glowing giants are the ultimate salespeople. Let’s dive into why Las Vegas billboards outshine traditional ads and how your business can ride their 24/7 energy wave.
** Why Las Vegas Billboards Never Take a Coffee Break
** 1. Tourists Don’t Have Bedtimes (and Neither Do Billboards)
- 42 million visitors flock to Vegas yearly. They’re sipping margaritas at noon, gambling at midnight, and shopping at 3 AM.
- Las Vegas billboards near hotspots like the Bellagio Fountains or Fremont Street catch eyes round the clock.Real Story:
A donut shop owner named Luis rented a billboard near the “Welcome to Vegas” sign. His message? “Jet Lagged? Sugar Fix Open 24/7!” Sales tripled—especially between 1 AM and 4 AM.** 2. You Can’t “Skip” a Billboard
** - Imagine this: You’re stuck in traffic on the Strip. Your phone’s dead. That Las Vegas billboard for air-conditioned massages? It’s your lifeline.
- Compare that to online ads: 47% of people skip them, and TikTok ads vanish in a scroll.- Vegas Thrives on Impulse
- Billboards tap into spontaneous decisions:
- “Let’s try that rooftop bar!”
- “Wait, free slot play? Let’s U-turn!”
- Traditional ads (like radio spots) fade fast. Billboards linger, nudging tourists to act now.
** 5 Reasons Your Business Needs a Vegas Billboard
** 1. Size Matters (And So Does Flash)
- Strip billboards can be taller than a 5-story building.
- Digital screens use LEDs so bright, they’re visible from space.Pro Tip:
A casino added fake “smoke” effects to their billboard for a Halloween promo. Traffic backed up for selfies—and bookings spiked.- No Language Barrier
- Vegas draws visitors from Tokyo, Berlin, São Paulo...
- A Las Vegas billboard with a giant cocktail emoji? Universal for “Drinks here!”
Case Study:
A Korean BBQ spot used a billboard of sizzling meat. No words. Just smoke visuals. Tourists followed the “aroma” straight to their door.- They’re Always in the Right Place, Right Time
- 6 AM: Joggers see smoothie ads.
- 3 PM: Pool partiers spot “Free Margarita” promos.
-
Midnight: Hangover clinics whisper, “We’ve got IVs.”
-
Instant Trust Boost
- A tiny online ad says “startup.” A glowing billboard says, “We’re Vegas royalty.”
Jake’s Win:
Jake’s tiny magic shop rented a billboard reading, “Real Tricks—Cheaper Than the Casino!” Tourists treated him like David Blaine.- QR Codes = Instant Customers
- “Scan for free parking!” → 1,000 scans in a weekend.
- “Tap to call a limo” → Rides booked before the light turns green.
** How to Make Your Vegas Billboard Irresistible
** Step 1: Claim Your Territory
- The Strip: Pricey but prime ($15k–$60k/month).
- Fremont Street: Quirky, cheaper ($5k–$20k), packed with partiers.
- Highway 15: Target road-trippers with “Almost There! Cold Beer Ahead!”Step 2: Keep It Stupid Simple
- Bad: “Experience Culinary Excellence at Our Artisanal Bistro!”
- Good: “24/7 Bacon Pancakes → Exit Here.”Maria’s Hack:
Maria’s tattoo parlor used a billboard with a flaming skull and three words: “Walk-Ins Welcome.” No phone number. “People just… show up,” she laughs.Step 3: Track Your Wins (Like a Vegas High Roller)
- QR Codes: “Scan for Free Slot Play!” → Track scans.
- Unique URLs: “Visit VegasPizza24.com” → Monitor traffic.
- Old-School: Count foot traffic. (“Did that bachelor party just roll in from our billboard? Yes.”)**FAQs ** 1. “How do I even measure if my billboard’s working? It’s not like online ads!”
Answer:
You’re right—it’s not just clicks and likes. But here’s how real businesses track success:
- QR Codes: Add a unique code like “Scan for Free Appetizer!” Track scans.
- Promo Codes: “Mention this billboard for 20% off!” (Works great for Uber drivers: “My passengers blurt it out mid-ride,” says driver Luis M.)
- Foot Traffic Spikes: Note sales surges after your ad goes live. A dispensary saw a 60% bump in visits after their “We’re Closer Than the Casino!” billboard.
- Social Media Tags: Encourage selfies with your billboard. A retro motel offered a free pool pass for tagged photos. Their Instagram exploded.- “Aren’t billboards old-school? My Gen Z customers live on TikTok!”
Answer:
Billboards in Vegas are anything but old-school. Here’s why: - Hybrid Campaigns: Pair billboards with geofenced mobile ads. Example: A billboard for a pool party says, “Scan to Pre-Order Drinks.” Users nearby get a TikTok-style ad on their phone.
- Instagrammable Designs: Quirky billboards go viral. The “Welcome to Vegas” sign is the most Instagrammed spot in the city. Mimic that vibe!
- Influencer Collabs: Pay a Vegas influencer to pose with your billboard. Their followers will hunt it down like a scavenger hunt.
Real Story:
A vintage clothing store’s billboard (“Find Your Retro Vibe → 2 Blocks East”) became a TikTok trend after a local influencer did a “thrift haul” video there.** 3. “What’s the biggest mistake businesses make with Vegas billboards?”
** Answer:
Trying to cram in too much info! Drivers have 5–7 seconds to read your ad. Avoid:
- Text Overload: “Grand Opening! 50% Off! Open 24/7! Call Now!” → Too much!
- Bland Designs: Gray text on a gray background? Yawn.
- Ignoring Locals: Tourists are 70% of viewers, but locals matter too. A gym’s billboard said, “Tired of Tourists? Work Out in Peace.” Memberships spiked.Fix It:
- Use 7 words max.
- Bold colors (red, yellow, neon pink).
- Add a clear call to action: “Turn Right Now!” or “Scan for Free Parking.”- “Do I need a permit? What if my ad gets rejected?”
Answer:
Yep, permits are a thing. The city bans: - Flashing Lights Near Residences: No strobes in suburban areas.
- Certain Content: No swear words, adult themes, or political fights.
How to Avoid Rejection:
- Work with local Outdoor Advertising companies—they know the rules.
- Submit designs early. One pizza joint’s ad was flagged for a pepperoni slice deemed “too suggestive.” They swapped it to a cheese pull… and it got approved.Conclusion: Let Your Business Shine All Night Long
At 5 AM, as the sun peeks over the desert, the Las Vegas billboards keep glowing. They’ve sold midnight pancakes, inspired shotgun weddings, and even talked someone out of a questionable tattoo (“Wait! Our Parlor’s Better → Next Exit”).These aren’t just ads—they’re part of Vegas’ heartbeat. So whether you’re slinging sushi, massages, or monster truck rides, remember: In a city that never sleeps, your billboard shouldn’t either.
Ready to Light Up the Night?
Find Las Vegas billboards near you today. And if you spot one that says, “Free High-Fives for Readers of This Article,” honk twice. It’s probably yours. -
 @ 6e0ea5d6:0327f353
2025-05-28 04:34:08
@ 6e0ea5d6:0327f353
2025-05-28 04:34:08Ascolta bene! It is more dignified to thirst alone in the desert than to share wine with someone who has no thirst for conquest.
On the silent path to success, it’s not the declared enemies who slow the march, but rather the friends. Not the noble or loyal ones, but the failures—those who carry a dull glint in their eyes, chronic laziness in their spirit, and the eternal excuse of bad luck in their pockets. Friendship, when poorly chosen, becomes a polished anchor, tied to your ankle with ropes named camaraderie.
Nothing weighs heavier on the journey than having to endure the failed and envious around you. It is a kind of emotional parasitism that begins with empathy and ends in stagnation. Those who live among the weak will crawl. Those who keep company with miserable friends, instead of striving to prosper, learn to curse wealth—not out of ethics, but out of envy. Mediocrity, my friend, is contagious. And it does not take root suddenly, but like a silent epidemic.
Ambition—that fire that burns in the bones of great men—will always seem like arrogance to the ears of the failed. Those who have never built anything, except arguments to justify their paralysis, will never understand the fury of someone born to conquer. And so, with smiles, they spit venom: “Calm down,” they say, “be content,” they advise. Hypocrites. What they call humility is nothing more than resignation to their own defeat.
To walk alone, with hunger and honor, is worth more than feasting at lavish tables at the cost of your own sweat, surrounded by parasites who toast your downfall with glasses full of praise. No one prospers where the conversation is filled with complaints, criticism, and envy. What does not build up, corrodes.
The rust of the weak is invisible at first—a bitter joke here, a veiled critique there. And before you know it, the structure is already rotten. Of the friendship, only the weight remains. Of the relationship, only exhaustion. The true enemy of success is the company of those who have failed and wish for you the same fate. These tragic figures—always tired, always victims—are masters of collective self-sabotage.
Feel no remorse in abandoning those who build nothing and consume everything. And in that abandonment, you become freer, stronger, and unbreakable.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ f9cf4e94:96abc355
2024-12-31 20:18:59
@ f9cf4e94:96abc355
2024-12-31 20:18:59Scuttlebutt foi iniciado em maio de 2014 por Dominic Tarr ( dominictarr ) como uma rede social alternativa off-line, primeiro para convidados, que permite aos usuários obter controle total de seus dados e privacidade. Secure Scuttlebutt (ssb) foi lançado pouco depois, o que coloca a privacidade em primeiro plano com mais recursos de criptografia.
Se você está se perguntando de onde diabos veio o nome Scuttlebutt:
Este termo do século 19 para uma fofoca vem do Scuttlebutt náutico: “um barril de água mantido no convés, com um buraco para uma xícara”. A gíria náutica vai desde o hábito dos marinheiros de se reunir pelo boato até a fofoca, semelhante à fofoca do bebedouro.

Marinheiros se reunindo em torno da rixa. ( fonte )
Dominic descobriu o termo boato em um artigo de pesquisa que leu.
Em sistemas distribuídos, fofocar é um processo de retransmissão de mensagens ponto a ponto; as mensagens são disseminadas de forma análoga ao “boca a boca”.
Secure Scuttlebutt é um banco de dados de feeds imutáveis apenas para acréscimos, otimizado para replicação eficiente para protocolos ponto a ponto. Cada usuário tem um log imutável somente para acréscimos no qual eles podem gravar. Eles gravam no log assinando mensagens com sua chave privada. Pense em um feed de usuário como seu próprio diário de bordo, como um diário de bordo (ou diário do capitão para os fãs de Star Trek), onde eles são os únicos autorizados a escrever nele, mas têm a capacidade de permitir que outros amigos ou colegas leiam ao seu diário de bordo, se assim o desejarem.
Cada mensagem possui um número de sequência e a mensagem também deve fazer referência à mensagem anterior por seu ID. O ID é um hash da mensagem e da assinatura. A estrutura de dados é semelhante à de uma lista vinculada. É essencialmente um log somente de acréscimo de JSON assinado. Cada item adicionado a um log do usuário é chamado de mensagem.
Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações. Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.

Estrutura de alto nível de um feed
Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar. Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência.
Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub.
Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.
Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de Pubs públicos em que todos podem participar . Explicaremos como ingressar em um posteriormente neste guia. Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais. Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.

Perspectivas dos participantes
Scuttlebot
O software Pub é conhecido como servidor Scuttlebutt (servidor ssb ), mas também é conhecido como “Scuttlebot” e
sbotna linha de comando. O servidor SSB adiciona comportamento de rede ao banco de dados Scuttlebutt (SSB). Estaremos usando o Scuttlebot ao longo deste tutorial.Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações. Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.

Estrutura de alto nível de um feed
Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar. Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência.
Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub.
Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.
Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de Pubs públicos em que todos podem participar . Explicaremos como ingressar em um posteriormente neste guia. Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais. Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.


Perspectivas dos participantes
Pubs - Hubs
Pubs públicos
| Pub Name | Operator | Invite Code | | ------------------------------------------------------------ | ------------------------------------------------------------ | ------------------------------------------------------------ | |
scuttle.us| @Ryan |scuttle.us:8008:@WqcuCOIpLtXFRw/9vOAQJti8avTZ9vxT9rKrPo8qG6o=.ed25519~/ZUi9Chpl0g1kuWSrmehq2EwMQeV0Pd+8xw8XhWuhLE=| | pub1.upsocial.com | @freedomrules |pub1.upsocial.com:8008:@gjlNF5Cyw3OKZxEoEpsVhT5Xv3HZutVfKBppmu42MkI=.ed25519~lMd6f4nnmBZEZSavAl4uahl+feajLUGqu8s2qdoTLi8=| | Monero Pub | @Denis |xmr-pub.net:8008:@5hTpvduvbDyMLN2IdzDKa7nx7PSem9co3RsOmZoyyCM=.ed25519~vQU+r2HUd6JxPENSinUWdfqrJLlOqXiCbzHoML9iVN4=| | FreeSocial | @Jarland |pub.freesocial.co:8008:@ofYKOy2p9wsaxV73GqgOyh6C6nRGFM5FyciQyxwBd6A=.ed25519~ye9Z808S3KPQsV0MWr1HL0/Sh8boSEwW+ZK+8x85u9w=| |ssb.vpn.net.br| @coffeverton |ssb.vpn.net.br:8008:@ze8nZPcf4sbdULvknEFOCbVZtdp7VRsB95nhNw6/2YQ=.ed25519~D0blTolH3YoTwSAkY5xhNw8jAOjgoNXL/+8ZClzr0io=| | gossip.noisebridge.info | Noisebridge Hackerspace @james.network |gossip.noisebridge.info:8008:@2NANnQVdsoqk0XPiJG2oMZqaEpTeoGrxOHJkLIqs7eY=.ed25519~JWTC6+rPYPW5b5zCion0gqjcJs35h6JKpUrQoAKWgJ4=|Pubs privados
Você precisará entrar em contato com os proprietários desses bares para receber um convite.
| Pub Name | Operator | Contact | | --------------------------------------------- | ------------------------------------------------------------ | ----------------------------------------------- | |
many.butt.nz| @dinosaur | mikey@enspiral.com | |one.butt.nz| @dinosaur | mikey@enspiral.com | |ssb.mikey.nz| @dinosaur | mikey@enspiral.com | | ssb.celehner.com | @cel | cel@celehner.com |Pubs muito grandes
Aviso: embora tecnicamente funcione usar um convite para esses pubs, você provavelmente se divertirá se o fizer devido ao seu tamanho (muitas coisas para baixar, risco para bots / spammers / idiotas)
| Pub Name | Operator | Invite Code | | --------------------------------------- | ----------------------------------------------- | ------------------------------------------------------------ | |
scuttlebutt.de| SolSoCoG |scuttlebutt.de:8008:@yeh/GKxlfhlYXSdgU7CRLxm58GC42za3tDuC4NJld/k=.ed25519~iyaCpZ0co863K9aF+b7j8BnnHfwY65dGeX6Dh2nXs3c=| |Lohn's Pub| @lohn |p.lohn.in:8018:@LohnKVll9HdLI3AndEc4zwGtfdF/J7xC7PW9B/JpI4U=.ed25519~z3m4ttJdI4InHkCtchxTu26kKqOfKk4woBb1TtPeA/s=| | Scuttle Space | @guil-dot | Visit scuttle.space | |SSB PeerNet US-East| timjrobinson |us-east.ssbpeer.net:8008:@sTO03jpVivj65BEAJMhlwtHXsWdLd9fLwyKAT1qAkc0=.ed25519~sXFc5taUA7dpGTJITZVDCRy2A9jmkVttsr107+ufInU=| | Hermies | s | net:hermies.club:8008~shs:uMYDVPuEKftL4SzpRGVyQxLdyPkOiX7njit7+qT/7IQ=:SSB+Room+PSK3TLYC2T86EHQCUHBUHASCASE18JBV24= |GUI - Interface Gráfica do Utilizador(Usuário)
Patchwork - Uma GUI SSB (Descontinuado)
Patchwork é o aplicativo de mensagens e compartilhamento descentralizado construído em cima do SSB . O protocolo scuttlebutt em si não mantém um conjunto de feeds nos quais um usuário está interessado, então um cliente é necessário para manter uma lista de feeds de pares em que seu respectivo usuário está interessado e seguindo.

Fonte: scuttlebutt.nz
Quando você instala e executa o Patchwork, você só pode ver e se comunicar com seus pares em sua rede local. Para acessar fora de sua LAN, você precisa se conectar a um Pub. Um pub é apenas para convidados e eles retransmitem mensagens entre você e seus pares fora de sua LAN e entre outros Pubs.
Lembre-se de que você precisa seguir alguém para receber mensagens dessa pessoa. Isso reduz o envio de mensagens de spam para os usuários. Os usuários só veem as respostas das pessoas que seguem. Os dados são sincronizados no disco para funcionar offline, mas podem ser sincronizados diretamente com os pares na sua LAN por wi-fi ou bluetooth.
Patchbay - Uma GUI Alternativa
Patchbay é um cliente de fofoca projetado para ser fácil de modificar e estender. Ele usa o mesmo banco de dados que Patchwork e Patchfoo , então você pode facilmente dar uma volta com sua identidade existente.

Planetary - GUI para IOS

Planetary é um app com pubs pré-carregados para facilitar integração.
Manyverse - GUI para Android

Manyverse é um aplicativo de rede social com recursos que você esperaria: posts, curtidas, perfis, mensagens privadas, etc. Mas não está sendo executado na nuvem de propriedade de uma empresa, em vez disso, as postagens de seus amigos e todos os seus dados sociais vivem inteiramente em seu telefone .
Fontes
-
https://scuttlebot.io/
-
https://decentralized-id.com/decentralized-web/scuttlebot/#plugins
-
https://medium.com/@miguelmota/getting-started-with-secure-scuttlebut-e6b7d4c5ecfd
-
Secure Scuttlebutt : um protocolo de banco de dados global.
-
-
 @ 1d7ff02a:d042b5be
2025-05-28 04:02:47
@ 1d7ff02a:d042b5be
2025-05-28 04:02:47For those who still don't truly understand Bitcoin, it means you still don't understand what money is, who creates it, and why humans need money.
It's a scam that the education system doesn't teach this important subject, while we spend almost our entire lives trying to earn money. Therefore, I recommend following the money and studying Bitcoin seriously.
Why Bitcoin Matters
Saving is the greatest discovery in human history
Before humans learned to save, we were just animals living day to day. Saving is what makes humans different from other animals — the ability to think about the future and store for later.
Saving created civilization itself
Without saving, there would be no cities, no science, no art. Everything we call "progress" comes from the ability to save.
Money is the greatest creation in human history
It is the tool that has allowed human civilization to advance to this day. Money is the best tool humans use for saving.
Bitcoin is the best money ever created
It is the most perfect money humans have ever created. No one can control, manipulate, destroy it, and it is truly limited like time in life.
Bitcoin is like a black hole
That will absorb all value from the damaged financial system. It will draw stability and value to itself. Everything of value will flow into Bitcoin eventually.
Bitcoin is like Buddhism discovering truth
It helps understand the root problems of the current financial system and the emergence of many problems in society, just like Buddha who understood all suffering and the causes of suffering.
Bitcoin is freedom
Money is power, money controls human behavior. When we have money that preserves value and cannot be controlled, we will have intellectual freedom, freedom of expression, and the power to choose.
The debt that humanity has created today would take another thousand years to pay off completely
There is no way out and it's heading toward serious collapse. Bitcoin is the light that will help prevent humanity from entering another dark age.
Bitcoin cannot steal your time
It cannot be created from nothing. Every Bitcoin requires real energy and time to create.
Bitcoin is insurance that protects against mismanagement
It helps protect against currency debasement, economic depression, and failed policies. Bitcoin will protect your value.
Bitcoin is going to absorb the world's value
Eventually, Bitcoin will become the store of value for the entire world. It will absorb wealth from all assets, all prices, and all investments.
Exit The Matrix
We live in a financial Matrix. Every day we wake up and go to work, thinking we're building a future for ourselves. But in reality, we're just giving energy to a system that extracts value from us every second. Bitcoin is the red pill — it will open your eyes to see the truth of the financial world. Central banks are the architects of this Matrix — they create money from nothing, and we have to work hard to get it.
The education system has deceived us greatly. They teach us to work for money, but never teach us what money is. We spend 12-16 years in school, then spend our entire lives earning money, but never know what it is, who creates it, and why it has value. This is the biggest scam in human history.
We are taught to be slaves of the system, but not taught to understand the system.
The Bitcoin standard will end war
When you can't print money for war anymore, war becomes too expensive.
We are entering the Bitcoin Renaissance era
An era of financial and intellectual revival. Bitcoin is creating a new class of humans. People who understand and hold Bitcoin will become a new class with true freedom.
The Path to Financial Truth
Follow the money trail and you will see the truth: - Who controls money printing? - Why do prices keep getting higher? - Why are the poor getting poorer and the rich getting richer?
All the answers lie in understanding money and Bitcoin.
Studying Bitcoin is not just about investment — it's about understanding the future of currency and human society.
Don't just work for money. Understand money. Study Bitcoin.
If you don't understand money, you will be a slave to the system forever. If you understand Bitcoin, you will gain freedom.
-
 @ 502ab02a:a2860397
2025-05-28 02:03:01
@ 502ab02a:a2860397
2025-05-28 02:03:01ยังมีอีกสิ่งหนึ่งที่มักซ่อนอยู่ในเมล็ดธัญพืช ถั่วเปลือกแข็ง และพืชตระกูลถั่วทั้งหลาย เป็นเหมือน “กล่องเก็บขุมทรัพย์” สำหรับชีวิตน้อยๆ ของพืชในวันที่จะเติบโต แต่พอสิ่งนี้หลุดเข้ามาในร่างกายมนุษย์ มันกลับถูกมองว่าเป็น “ขโมย” ขโมยแร่ธาตุไปจากร่างกายเรา เจ้าสิ่งนั้นคือ “กรดไฟติก” หรือ phytic acid นั่นเองครับ
กรดไฟติกเป็นสารอินทรีย์ที่พืชสร้างขึ้นเพื่อเก็บสะสมฟอสฟอรัสไว้ใช้ตอนงอกงามในอนาคต มันเปรียบเหมือนกระปุกออมสินของเมล็ดพืช พวกเมล็ดถั่วดำ ข้าวโพด ข้าวกล้อง ข้าวโอ๊ต เมล็ดทานตะวัน อัลมอนด์ ไปจนถึงเต้าหู้ ถั่วเหลือง และธัญพืชต่างๆ ล้วนมีกรดไฟติกอยู่ไม่น้อย โดยเฉพาะถ้าเป็น “ธัญพืชเต็มเมล็ด” ที่ไม่ผ่านการขัดสีแบบที่หลายๆคนชอบ นั่นเพราะเยื่อหุ้มเมล็ดคือที่เก็บเจ้าตัวนี้ไว้
หลายคนคงคิดว่า อ้าวแล้วเจ้ากรดไฟติกทำไมถึงมีชื่อเสียงไม่ค่อยดีนัก? คำตอบอยู่ที่ “ความสามารถในการจับแร่ธาตุ” ของมันนี่แหละครับ
กรดไฟติกเป็นเหมือนแม่เหล็กเล็กๆ ที่สามารถจับตัวกับแร่ธาตุต่างๆ ได้ดี โดยเฉพาะ “แร่ธาตุบวกสอง” ทั้งหลาย แร่ธาตุบวกสอง คือ แร่ธาตุที่เวลาอยู่ในร่างกายจะอยู่ในรูปของไอออนที่มีประจุไฟฟ้า บวก 2 (เขียนว่า ²⁺) หรือพูดอีกแบบคือ มันเสียอิเล็กตรอนออกไป 2 ตัว เลยกลายเป็นไอออนที่มีพลังบวก 2 หน่วย กรดไฟติก หรือ แทนนิน จะทำตัวเป็น "แม่เหล็ก" ดูดแร่ธาตุออกไป มันมักจะจับกับแร่ธาตุที่มีประจุบวก โดยเฉพาะพวกที่ประจุบวกแรงๆ แบบ บวกสอง (²⁺) นี่แหละ เพราะจับแน่น จับเหนียว ยิ่งบวกเยอะยิ่งจับดี เหมือนแช่แม่เหล็กลงไปในกล่องโลหะ เช่น ธาตุเหล็ก สังกะสี แมกนีเซียม แคลเซียม และทองแดง พอมันจับเสร็จแล้ว ร่างกายเราก็ไม่สามารถดูดซึมแร่ธาตุพวกนี้เข้าไปได้ เพราะมันเปลี่ยนสภาพกลายเป็นของจับคู่ที่ลำไส้ไม่รู้จัก ไม่รู้จะพาเข้าร่างกายยังไง สุดท้ายก็ต้องโบกมือลาไปพร้อมของเสีย
พวกที่เป็น บวกสาม (³⁺) อย่างเช่น อลูมิเนียม (Al³⁺) หรือ เหล็กเฟอริก (Fe³⁺) จะจับแน่นมาก ถึงขั้นอาจเกิด “ตกตะกอน” แบบไม่ละลายน้ำเลยทีเดียว พวกนี้ลำไส้ไม่สามารถดูดซึมได้เลย ในขณะที่แร่ธาตุบวกหนึ่ง โซเดียม (Na⁺) โพแทสเซียม (K⁺) ประจุบวกแค่ +1 จับกับกรดไฟติกได้น้อยกว่า
ในแง่นี้กรดไฟติกเลยถูกเรียกว่า “สารต้านสารอาหาร” หรือ anti-nutrient เพราะมันต้านไม่ให้ร่างกายได้แร่ธาตุที่ควรจะได้ แต่อย่าเพิ่งตัดสินมันเหมือนผู้ร้าย เพราะในขณะที่กรดไฟติกอาจขโมยแร่ธาตุบางตัวจากร่างกาย มันก็มีคุณสมบัติน่าสนใจที่ดูจะเป็นคุณงามความดีของมันเหมือนกัน เช่น มันสามารถจับกับโลหะหนักบางชนิด เช่น ตะกั่ว หรือแคดเมียม ที่อาจปนเปื้อนในอาหาร แล้วพาออกไปจากร่างกายก่อนที่สิ่งเหล่านั้นจะทำร้ายเรา
และอีกด้านหนึ่งที่กำลังเป็นที่สนใจคือ ฤทธิ์ต้านอนุมูลอิสระของกรดไฟติก มันอาจช่วยลดการอักเสบ หรือยับยั้งการเติบโตของเซลล์มะเร็งบางชนิดในระดับเซลล์ได้ มีงานวิจัยที่พบว่ามันอาจไปจับกับธาตุเหล็กส่วนเกินที่ว่ายอยู่ในเลือด ซึ่งเป็นตัวเร่งปฏิกิริยาอนุมูลอิสระ คล้ายช่วย “เก็บเศษเหล็กที่ลอยไปมาบนทางด่วนหลอดเลือด” ให้ปลอดภัยขึ้นอีกนิด
แต่ทั้งนี้ทั้งนั้น อยากให้คิดแบบนี้ครับว่า กรดไฟติกคือคนแปลกหน้าที่ “บางมื้อก็มีประโยชน์ บางมื้อก็ทำให้เราขาดของดี” สิ่งสำคัญอยู่ที่ “สภาวะแวดล้อมของมื้ออาหาร” ถ้าอาหารในมื้อมีแร่ธาตุไม่มากนัก แล้วกรดไฟติกเข้ามาเยอะ มันก็ยิ่งลดโอกาสดูดซึมแร่ธาตุเหล่านั้น แต่ถ้ามื้ออาหารมีความหลากหลาย โปรตีนเพียงพอ วิตามิน C อยู่ครบ ก็ช่วยเพิ่มการดูดซึมธาตุเหล็กได้ดีขึ้น เพราะมันเปลี่ยนเหล็กให้อยู่ในรูปแบบที่ร่างกายดูดซึมง่ายขึ้น
แล้วเราจะจัดการยังไงกับกรดไฟติกในครัวแบบบ้านเรา?
วิธีพื้นบ้านมีมาแต่โบราณแล้วนั่นคือ -แช่น้ำ ก่อนหุงข้าวกล้อง หรือแช่ถั่วก่อนนำไปต้ม จะช่วยลดกรดไฟติกได้ระดับหนึ่ง เพราะมีเอนไซม์ที่ชื่อว่า phytase ซึ่งจะเริ่มทำงานเมื่อพืชได้รับน้ำและอุณหภูมิพอเหมาะ -การหมัก เช่น หมักแป้งข้าวเปลือกทำขนม หรือการหมักเต้าหู้ ก็เป็นวิธีดั้งเดิมที่ช่วยลดกรดไฟติกลงได้มาก เพราะเอนไซม์ของจุลินทรีย์ในกระบวนการหมักจะช่วยย่อยกรดไฟติกให้ลดลง -การงอก หรือ sprouting คือการทำให้เมล็ดพืชเริ่มต้นชีวิตใหม่ เช่น ถั่วงอก ข้าวกล้องงอก วิธีนี้ลดกรดไฟติกได้ดีมาก เพราะ phytase ที่อยู่ในพืชจะถูกกระตุ้นให้ทำงานสูงสุดตอนพืชเริ่มงอก
ข้อมูลคร่าวๆ บอกว่า วิธีเหล่านี้อาจลดกรดไฟติกลงได้ 30-90% ขึ้นกับชนิดของพืช และระยะเวลาที่ใช้
แต่ต้องรู้ไว้ด้วยว่า… การลดกรดไฟติกก็อาจทำให้พลังงานสำรองหรือสารอาหารบางตัวในพืชหายไปด้วยเช่นกัน เช่น วิตามิน B และสารต้านอนุมูลอิสระบางชนิด จึงควรใช้วิธีที่พอเหมาะ ไม่ถึงกับฆ่าความดีของพืชหมด
ดังนั้นเช่นกันครับว่า กรดไฟติกไม่ใช่ศัตรู ไม่ใช่เทพเจ้า แต่คือ “สมการ” ที่ต้องรู้จักแก้ไขให้เหมาะกับมื้ออาหารของเรา ถ้าเฮียเลือกกินแบบ animal-based อยู่แล้ว แร่ธาตุสำคัญส่วนใหญ่ก็ได้จากเนื้อสัตว์แบบที่ดูดซึมได้ดีอยู่แล้ว กรดไฟติกจากพืชที่กินพอประมาณก็อาจไม่ได้ร้ายแรงอะไรนัก เพียงแต่ต้องรู้ทันและจัดการให้พอดี ไม่ให้มันกลายเป็นตัวฉุดไม่ให้ร่างกายดูดซึมของดี
สุดท้าย เหมือนชีวิตเรานี่แหละ… “ทุกอย่างมีมุมมืดและมุมสว่าง อยู่ที่ว่าเราจัดแสงยังไงให้แม้แต่เงาก็กลายเป็นพลังของชีวิตเรา” #โรงบ่มสุขภาพ #HealthyHut #pirateketo #ตำรับเอ๋ #siripun #siamstr
/เฮียเอง
-
 @ e97aaffa:2ebd765d
2024-12-31 16:47:12
@ e97aaffa:2ebd765d
2024-12-31 16:47:12Último dia do ano, momento para tirar o pó da bola de cristal, para fazer reflexões, previsões e desejos para o próximo ano e seguintes.
Ano após ano, o Bitcoin evoluiu, foi ultrapassando etapas, tornou-se cada vez mais mainstream. Está cada vez mais difícil fazer previsões sobre o Bitcoin, já faltam poucas barreiras a serem ultrapassadas e as que faltam são altamente complexas ou tem um impacto profundo no sistema financeiro ou na sociedade. Estas alterações profundas tem que ser realizadas lentamente, porque uma alteração rápida poderia resultar em consequências terríveis, poderia provocar um retrocesso.
Código do Bitcoin
No final de 2025, possivelmente vamos ter um fork, as discussões sobre os covenants já estão avançadas, vão acelerar ainda mais. Já existe um consenso relativamente alto, a favor dos covenants, só falta decidir que modelo será escolhido. Penso que até ao final do ano será tudo decidido.
Depois dos covenants, o próximo foco será para a criptografia post-quantum, que será o maior desafio que o Bitcoin enfrenta. Criar uma criptografia segura e que não coloque a descentralização em causa.
Espero muito de Ark, possivelmente a inovação do ano, gostaria de ver o Nostr a furar a bolha bitcoinheira e que o Cashu tivesse mais reconhecimento pelos bitcoiners.
Espero que surjam avanços significativos no BitVM2 e BitVMX.
Não sei o que esperar das layer 2 de Bitcoin, foram a maior desilusão de 2024. Surgiram com muita força, mas pouca coisa saiu do papel, foi uma mão cheia de nada. Uma parte dos projetos caiu na tentação da shitcoinagem, na criação de tokens, que tem um único objetivo, enriquecer os devs e os VCs.
Se querem ser levados a sério, têm que ser sérios.
“À mulher de César não basta ser honesta, deve parecer honesta”
Se querem ter o apoio dos bitcoiners, sigam o ethos do Bitcoin.
Neste ponto a atitude do pessoal da Ark é exemplar, em vez de andar a chorar no Twitter para mudar o código do Bitcoin, eles colocaram as mãos na massa e criaram o protocolo. É claro que agora está meio “coxo”, funciona com uma multisig ou com os covenants na Liquid. Mas eles estão a criar um produto, vão demonstrar ao mercado que o produto é bom e útil. Com a adoção, a comunidade vai perceber que o Ark necessita dos covenants para melhorar a interoperabilidade e a soberania.
É este o pensamento certo, que deveria ser seguido pelos restantes e futuros projetos. É seguir aquele pensamento do J.F. Kennedy:
“Não perguntem o que é que o vosso país pode fazer por vocês, perguntem o que é que vocês podem fazer pelo vosso país”
Ou seja, não fiquem à espera que o bitcoin mude, criem primeiro as inovações/tecnologia, ganhem adoção e depois demonstrem que a alteração do código camada base pode melhorar ainda mais o vosso projeto. A necessidade é que vai levar a atualização do código.
Reservas Estratégicas de Bitcoin
Bancos centrais
Com a eleição de Trump, emergiu a ideia de uma Reserva Estratégia de Bitcoin, tornou este conceito mainstream. Foi um pivot, a partir desse momento, foram enumerados os políticos de todo o mundo a falar sobre o assunto.
A Senadora Cynthia Lummis foi mais além e propôs um programa para adicionar 200 mil bitcoins à reserva ao ano, até 1 milhão de Bitcoin. Só que isto está a criar uma enorme expectativa na comunidade, só que pode resultar numa enorme desilusão. Porque no primeiro ano, o Trump em vez de comprar os 200 mil, pode apenas adicionar na reserva, os 198 mil que o Estado já tem em sua posse. Se isto acontecer, possivelmente vai resultar numa forte queda a curto prazo. Na minha opinião os bancos centrais deveriam seguir o exemplo de El Salvador, fazer um DCA diário.
Mais que comprar bitcoin, para mim, o mais importante é a criação da Reserva, é colocar o Bitcoin ao mesmo nível do ouro, o impacto para o resto do mundo será tremendo, a teoria dos jogos na sua plenitude. Muitos outros bancos centrais vão ter que comprar, para não ficarem atrás, além disso, vai transmitir uma mensagem à generalidade da população, que o Bitcoin é “afinal é algo seguro, com valor”.
Mas não foi Trump que iniciou esta teoria dos jogos, mas sim foi a primeira vítima dela. É o próprio Trump que o admite, que os EUA necessitam da reserva para não ficar atrás da China. Além disso, desde que os EUA utilizaram o dólar como uma arma, com sanção contra a Rússia, surgiram boatos de que a Rússia estaria a utilizar o Bitcoin para transações internacionais. Que foram confirmados recentemente, pelo próprio governo russo. Também há poucos dias, ainda antes deste reconhecimento público, Putin elogiou o Bitcoin, ao reconhecer que “Ninguém pode proibir o bitcoin”, defendendo como uma alternativa ao dólar. A narrativa está a mudar.
Já existem alguns países com Bitcoin, mas apenas dois o fizeram conscientemente (El Salvador e Butão), os restantes têm devido a apreensões. Hoje são poucos, mas 2025 será o início de uma corrida pelos bancos centrais. Esta corrida era algo previsível, o que eu não esperava é que acontecesse tão rápido.
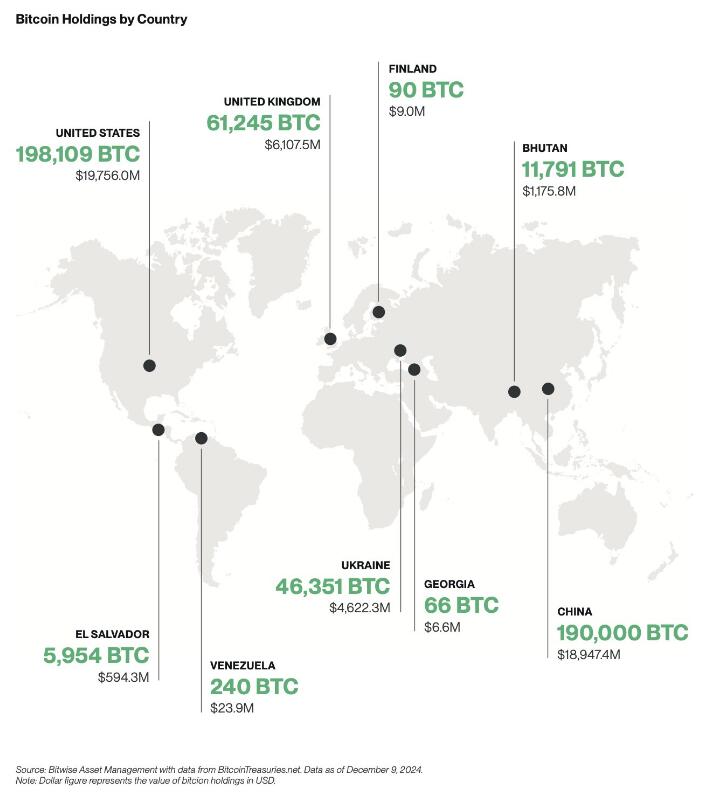
Empresas
A criação de reservas estratégicas não vai ficar apenas pelos bancos centrais, também vai acelerar fortemente nas empresas em 2025.

Mas as empresas não vão seguir a estratégia do Saylor, vão comprar bitcoin sem alavancagem, utilizando apenas os tesouros das empresas, como uma proteção contra a inflação. Eu não sou grande admirador do Saylor, prefiro muito mais, uma estratégia conservadora, sem qualquer alavancagem. Penso que as empresas vão seguir a sugestão da BlackRock, que aconselha um alocações de 1% a 3%.
Penso que 2025, ainda não será o ano da entrada das 6 magníficas (excepto Tesla), será sobretudo empresas de pequena e média dimensão. As magníficas ainda tem uma cota muito elevada de shareholders com alguma idade, bastante conservadores, que têm dificuldade em compreender o Bitcoin, foi o que aconteceu recentemente com a Microsoft.
Também ainda não será em 2025, talvez 2026, a inclusão nativamente de wallet Bitcoin nos sistema da Apple Pay e da Google Pay. Seria um passo gigante para a adoção a nível mundial.
ETFs
Os ETFs para mim são uma incógnita, tenho demasiadas dúvidas, como será 2025. Este ano os inflows foram superiores a 500 mil bitcoins, o IBIT foi o lançamento de ETF mais bem sucedido da história. O sucesso dos ETFs, deve-se a 2 situações que nunca mais se vão repetir. O mercado esteve 10 anos à espera pela aprovação dos ETFs, a procura estava reprimida, isso foi bem notório nos primeiros meses, os inflows foram brutais.
Também se beneficiou por ser um mercado novo, não existia orderbook de vendas, não existia um mercado interno, praticamente era só inflows. Agora o mercado já estabilizou, a maioria das transações já são entre clientes dos próprios ETFs. Agora só uma pequena percentagem do volume das transações diárias vai resultar em inflows ou outflows.
Estes dois fenómenos nunca mais se vão repetir, eu não acredito que o número de inflows em BTC supere os número de 2024, em dólares vai superar, mas em btc não acredito que vá superar.
Mas em 2025 vão surgir uma infindável quantidade de novos produtos, derivativos, novos ETFs de cestos com outras criptos ou cestos com ativos tradicionais. O bitcoin será adicionado em produtos financeiros já existentes no mercado, as pessoas vão passar a deter bitcoin, sem o saberem.
Com o fim da operação ChokePoint 2.0, vai surgir uma nova onda de adoção e de produtos financeiros. Possivelmente vamos ver bancos tradicionais a disponibilizar produtos ou serviços de custódia aos seus clientes.
Eu adoraria ver o crescimento da adoção do bitcoin como moeda, só que a regulamentação não vai ajudar nesse processo.
Preço
Eu acredito que o topo deste ciclo será alcançado no primeiro semestre, posteriormente haverá uma correção. Mas desta vez, eu acredito que a correção será muito menor que as anteriores, inferior a 50%, esta é a minha expectativa. Espero estar certo.
Stablecoins de dólar
Agora saindo um pouco do universo do Bitcoin, acho importante destacar as stablecoins.
No último ciclo, eu tenho dividido o tempo, entre continuar a estudar o Bitcoin e estudar o sistema financeiro, as suas dinâmicas e o comportamento humano. Isto tem sido o meu foco de reflexão, imaginar a transformação que o mundo vai sofrer devido ao padrão Bitcoin. É uma ilusão acreditar que a transição de um padrão FIAT para um padrão Bitcoin vai ser rápida, vai existir um processo transitório que pode demorar décadas.
Com a re-entrada de Trump na Casa Branca, prometendo uma política altamente protecionista, vai provocar uma forte valorização do dólar, consequentemente as restantes moedas do mundo vão derreter. Provocando uma inflação generalizada, gerando uma corrida às stablecoins de dólar nos países com moedas mais fracas. Trump vai ter uma política altamente expansionista, vai exportar dólares para todo o mundo, para financiar a sua própria dívida. A desigualdade entre os pobres e ricos irá crescer fortemente, aumentando a possibilidade de conflitos e revoltas.
“Casa onde não há pão, todos ralham e ninguém tem razão”
Será mais lenha, para alimentar a fogueira, vai gravar os conflitos geopolíticos já existentes, ficando as sociedade ainda mais polarizadas.
Eu acredito que 2025, vai haver um forte crescimento na adoção das stablecoins de dólares, esse forte crescimento vai agravar o problema sistémico que são as stablecoins. Vai ser o início do fim das stablecoins, pelo menos, como nós conhecemos hoje em dia.
Problema sistémico
O sistema FIAT não nasceu de um dia para outro, foi algo que foi construído organicamente, ou seja, foi evoluindo ao longo dos anos, sempre que havia um problema/crise, eram criadas novas regras ou novas instituições para minimizar os problemas. Nestes quase 100 anos, desde os acordos de Bretton Woods, a evolução foram tantas, tornaram o sistema financeiro altamente complexo, burocrático e nada eficiente.
Na prática é um castelo de cartas construído sobre outro castelo de cartas e que por sua vez, foi construído sobre outro castelo de cartas.
As stablecoins são um problema sistémico, devido às suas reservas em dólares e o sistema financeiro não está preparado para manter isso seguro. Com o crescimento das reservas ao longo dos anos, foi se agravando o problema.
No início a Tether colocava as reservas em bancos comerciais, mas com o crescimento dos dólares sob gestão, criou um problema nos bancos comerciais, devido à reserva fracionária. Essas enormes reservas da Tether estavam a colocar em risco a própria estabilidade dos bancos.
A Tether acabou por mudar de estratégia, optou por outros ativos, preferencialmente por títulos do tesouro/obrigações dos EUA. Só que a Tether continua a crescer e não dá sinais de abrandamento, pelo contrário.
Até o próprio mundo cripto, menosprezava a gravidade do problema da Tether/stablecoins para o resto do sistema financeiro, porque o marketcap do cripto ainda é muito pequeno. É verdade que ainda é pequeno, mas a Tether não o é, está no top 20 dos maiores detentores de títulos do tesouros dos EUA e está ao nível dos maiores bancos centrais do mundo. Devido ao seu tamanho, está a preocupar os responsáveis/autoridades/reguladores dos EUA, pode colocar em causa a estabilidade do sistema financeiro global, que está assente nessas obrigações.
Os títulos do tesouro dos EUA são o colateral mais utilizado no mundo, tanto por bancos centrais, como por empresas, é a charneira da estabilidade do sistema financeiro. Os títulos do tesouro são um assunto muito sensível. Na recente crise no Japão, do carry trade, o Banco Central do Japão tentou minimizar a desvalorização do iene através da venda de títulos dos EUA. Esta operação, obrigou a uma viagem de emergência, da Secretaria do Tesouro dos EUA, Janet Yellen ao Japão, onde disponibilizou liquidez para parar a venda de títulos por parte do Banco Central do Japão. Essa forte venda estava desestabilizando o mercado.
Os principais detentores de títulos do tesouros são institucionais, bancos centrais, bancos comerciais, fundo de investimento e gestoras, tudo administrado por gestores altamente qualificados, racionais e que conhecem a complexidade do mercado de obrigações.
O mundo cripto é seu oposto, é naife com muita irracionalidade e uma forte pitada de loucura, na sua maioria nem faz a mínima ideia como funciona o sistema financeiro. Essa irracionalidade pode levar a uma “corrida bancária”, como aconteceu com o UST da Luna, que em poucas horas colapsou o projeto. Em termos de escala, a Luna ainda era muito pequena, por isso, o problema ficou circunscrito ao mundo cripto e a empresas ligadas diretamente ao cripto.
Só que a Tether é muito diferente, caso exista algum FUD, que obrigue a Tether a desfazer-se de vários biliões ou dezenas de biliões de dólares em títulos num curto espaço de tempo, poderia provocar consequências terríveis em todo o sistema financeiro. A Tether é grande demais, é já um problema sistémico, que vai agravar-se com o crescimento em 2025.
Não tenham dúvidas, se existir algum problema, o Tesouro dos EUA vai impedir a venda dos títulos que a Tether tem em sua posse, para salvar o sistema financeiro. O problema é, o que vai fazer a Tether, se ficar sem acesso às venda das reservas, como fará o redeem dos dólares?
Como o crescimento do Tether é inevitável, o Tesouro e o FED estão com um grande problema em mãos, o que fazer com o Tether?
Mas o problema é que o atual sistema financeiro é como um curto cobertor: Quanto tapas a cabeça, destapas os pés; Ou quando tapas os pés, destapas a cabeça. Ou seja, para resolver o problema da guarda reservas da Tether, vai criar novos problemas, em outros locais do sistema financeiro e assim sucessivamente.
Conta mestre
Uma possível solução seria dar uma conta mestre à Tether, dando o acesso direto a uma conta no FED, semelhante à que todos os bancos comerciais têm. Com isto, a Tether deixaria de necessitar os títulos do tesouro, depositando o dinheiro diretamente no banco central. Só que isto iria criar dois novos problemas, com o Custodia Bank e com o restante sistema bancário.
O Custodia Bank luta há vários anos contra o FED, nos tribunais pelo direito a ter licença bancária para um banco com full-reserves. O FED recusou sempre esse direito, com a justificativa que esse banco, colocaria em risco toda a estabilidade do sistema bancário existente, ou seja, todos os outros bancos poderiam colapsar. Perante a existência em simultâneo de bancos com reserva fracionária e com full-reserves, as pessoas e empresas iriam optar pelo mais seguro. Isso iria provocar uma corrida bancária, levando ao colapso de todos os bancos com reserva fracionária, porque no Custodia Bank, os fundos dos clientes estão 100% garantidos, para qualquer valor. Deixaria de ser necessário limites de fundos de Garantia de Depósitos.
Eu concordo com o FED nesse ponto, que os bancos com full-reserves são uma ameaça a existência dos restantes bancos. O que eu discordo do FED, é a origem do problema, o problema não está nos bancos full-reserves, mas sim nos que têm reserva fracionária.
O FED ao conceder uma conta mestre ao Tether, abre um precedente, o Custodia Bank irá o aproveitar, reclamando pela igualdade de direitos nos tribunais e desta vez, possivelmente ganhará a sua licença.
Ainda há um segundo problema, com os restantes bancos comerciais. A Tether passaria a ter direitos similares aos bancos comerciais, mas os deveres seriam muito diferentes. Isto levaria os bancos comerciais aos tribunais para exigir igualdade de tratamento, é uma concorrência desleal. Isto é o bom dos tribunais dos EUA, são independentes e funcionam, mesmo contra o estado. Os bancos comerciais têm custos exorbitantes devido às políticas de compliance, como o KYC e AML. Como o governo não vai querer aliviar as regras, logo seria a Tether, a ser obrigada a fazer o compliance dos seus clientes.
A obrigação do KYC para ter stablecoins iriam provocar um terramoto no mundo cripto.
Assim, é pouco provável que seja a solução para a Tether.
FED
Só resta uma hipótese, ser o próprio FED a controlar e a gerir diretamente as stablecoins de dólar, nacionalizado ou absorvendo as existentes. Seria uma espécie de CBDC. Isto iria provocar um novo problema, um problema diplomático, porque as stablecoins estão a colocar em causa a soberania monetária dos outros países. Atualmente as stablecoins estão um pouco protegidas porque vivem num limbo jurídico, mas a partir do momento que estas são controladas pelo governo americano, tudo muda. Os países vão exigir às autoridades americanas medidas que limitem o uso nos seus respectivos países.
Não existe uma solução boa, o sistema FIAT é um castelo de cartas, qualquer carta que se mova, vai provocar um desmoronamento noutro local. As autoridades não poderão adiar mais o problema, terão que o resolver de vez, senão, qualquer dia será tarde demais. Se houver algum problema, vão colocar a responsabilidade no cripto e no Bitcoin. Mas a verdade, a culpa é inteiramente dos políticos, da sua incompetência em resolver os problemas a tempo.
Será algo para acompanhar futuramente, mas só para 2026, talvez…
É curioso, há uns anos pensava-se que o Bitcoin seria a maior ameaça ao sistema ao FIAT, mas afinal, a maior ameaça aos sistema FIAT é o próprio FIAT(stablecoins). A ironia do destino.
Isto é como uma corrida, o Bitcoin é aquele atleta que corre ao seu ritmo, umas vezes mais rápido, outras vezes mais lento, mas nunca pára. O FIAT é o atleta que dá tudo desde da partida, corre sempre em velocidade máxima. Só que a vida e o sistema financeiro não é uma prova de 100 metros, mas sim uma maratona.
Europa
2025 será um ano desafiante para todos europeus, sobretudo devido à entrada em vigor da regulamentação (MiCA). Vão começar a sentir na pele a regulamentação, vão agravar-se os problemas com os compliance, problemas para comprovar a origem de fundos e outras burocracias. Vai ser lindo.
O Travel Route passa a ser obrigatório, os europeus serão obrigados a fazer o KYC nas transações. A Travel Route é uma suposta lei para criar mais transparência, mas prática, é uma lei de controle, de monitorização e para limitar as liberdades individuais dos cidadãos.
O MiCA também está a colocar problemas nas stablecoins de Euro, a Tether para já preferiu ficar de fora da europa. O mais ridículo é que as novas regras obrigam os emissores a colocar 30% das reservas em bancos comerciais. Os burocratas europeus não compreendem que isto coloca em risco a estabilidade e a solvência dos próprios bancos, ficam propensos a corridas bancárias.
O MiCA vai obrigar a todas as exchanges a estar registadas em solo europeu, ficando vulnerável ao temperamento dos burocratas. Ainda não vai ser em 2025, mas a UE vai impor políticas de controle de capitais, é inevitável, as exchanges serão obrigadas a usar em exclusividade stablecoins de euro, as restantes stablecoins serão deslistadas.
Todas estas novas regras do MiCA, são extremamente restritas, não é para garantir mais segurança aos cidadãos europeus, mas sim para garantir mais controle sobre a população. A UE está cada vez mais perto da autocracia, do que da democracia. A minha única esperança no horizonte, é que o sucesso das políticas cripto nos EUA, vai obrigar a UE a recuar e a aligeirar as regras, a teoria dos jogos é implacável. Mas esse recuo, nunca acontecerá em 2025, vai ser um longo período conturbado.
Recessão
Os mercados estão todos em máximos históricos, isto não é sustentável por muito tempo, suspeito que no final de 2025 vai acontecer alguma correção nos mercados. A queda só não será maior, porque os bancos centrais vão imprimir dinheiro, muito dinheiro, como se não houvesse amanhã. Vão voltar a resolver os problemas com a injeção de liquidez na economia, é empurrar os problemas com a barriga, em de os resolver. Outra vez o efeito Cantillon.
Será um ano muito desafiante a nível político, onde o papel dos políticos será fundamental. A crise política na França e na Alemanha, coloca a UE órfã, sem um comandante ao leme do navio. 2025 estará condicionado pelas eleições na Alemanha, sobretudo no resultado do AfD, que podem colocar em causa a propriedade UE e o euro.
Possivelmente, só o fim da guerra poderia minimizar a crise, algo que é muito pouco provável acontecer.
Em Portugal, a economia parece que está mais ou menos equilibrada, mas começam a aparecer alguns sinais preocupantes. Os jogos de sorte e azar estão em máximos históricos, batendo o recorde de 2014, época da grande crise, não é um bom sinal, possivelmente já existe algum desespero no ar.
A Alemanha é o motor da Europa, quanto espirra, Portugal constipa-se. Além do problema da Alemanha, a Espanha também está à beira de uma crise, são os países que mais influenciam a economia portuguesa.
Se existir uma recessão mundial, terá um forte impacto no turismo, que é hoje em dia o principal motor de Portugal.
Brasil
Brasil é algo para acompanhar em 2025, sobretudo a nível macro e a nível político. Existe uma possibilidade de uma profunda crise no Brasil, sobretudo na sua moeda. O banco central já anda a queimar as reservas para minimizar a desvalorização do Real.

Sem mudanças profundas nas políticas fiscais, as reservas vão se esgotar. As políticas de controle de capitais são um cenário plausível, será interesse de acompanhar, como o governo irá proceder perante a existência do Bitcoin e stablecoins. No Brasil existe um forte adoção, será um bom case study, certamente irá repetir-se em outros países num futuro próximo.
Os próximos tempos não serão fáceis para os brasileiros, especialmente para os que não têm Bitcoin.
Blockchain
Em 2025, possivelmente vamos ver os primeiros passos da BlackRock para criar a primeira bolsa de valores, exclusivamente em blockchain. Eu acredito que a BlackRock vai criar uma própria blockchain, toda controlada por si, onde estarão os RWAs, para fazer concorrência às tradicionais bolsas de valores. Será algo interessante de acompanhar.
Estas são as minhas previsões, eu escrevi isto muito em cima do joelho, certamente esqueci-me de algumas coisas, se for importante acrescentarei nos comentários. A maioria das previsões só acontecerá após 2025, mas fica aqui a minha opinião.
Isto é apenas a minha opinião, Don’t Trust, Verify!
-
 @ 254f56d7:f2c38100
2024-12-30 07:38:27
@ 254f56d7:f2c38100
2024-12-30 07:38:27Vamos ver seu funcionamento

-
 @ 502ab02a:a2860397
2025-05-28 01:57:42
@ 502ab02a:a2860397
2025-05-28 01:57:42ในปี 2013 ณ กรุงลอนดอน แฮมเบอร์เกอร์หน้าตาดูธรรมดาแต่ไม่ธรรมดาชิ้นหนึ่งได้ถูกจัดวางอย่างสง่างามบนจานสีขาวในงานแถลงข่าวระดับโลก ไม่ใช่เพราะมันแพงเกินเหตุที่ตั้งราคาที่ 330,000 ดอลลาร์ต่อชิ้น แต่เพราะมันไม่เคยเกิดขึ้นมาก่อนในประวัติศาสตร์นี่คือ “เนื้อเพาะเลี้ยง” (cultured meat) ชิ้นแรกของโลกที่เติบโตมาจากเซลล์ ไม่ใช่จากสัตว์ทั้งตัว
เบื้องหลังอาหารชิ้นนี้คือชายชาวดัตช์คนหนึ่ง ชื่อว่า มาร์ค โพสต์ (Mark Post) นักวิทยาศาสตร์ด้านสรีรวิทยาหลอดเลือด ซึ่งไม่ได้มีดีกรีจากแค่มหาวิทยาลัย แต่มีความฝันที่อยากจะสร้างอาหารจากเทคโนโลยีเพื่ออนาคต เขาเริ่มต้นจากห้องทดลองเล็กๆ ที่มหาวิทยาลัย Maastricht ในประเทศเนเธอร์แลนด์ โดยเชื่อว่าการเพาะเลี้ยงเนื้อจากเซลล์ต้นกำเนิดของวัวจะสามารถลดผลกระทบด้านสิ่งแวดล้อมจากอุตสาหกรรมเนื้อสัตว์ได้
แต่กว่าจะมีแฮมเบอร์เกอร์เพาะเลี้ยงได้หนึ่งชิ้น เขาต้องเพาะเลี้ยงเส้นใยกล้ามเนื้อเล็กๆ มากกว่า 20,000 เส้น นำมารวมกัน ประกอบโครง สร้างรูปร่าง คล้ายกับงานศิลปะทางวิทยาศาสตร์ ใช้เวลาเป็นเดือน แถมกระบวนการทั้งหมดต้องอยู่ในสภาพปลอดเชื้อราวกับโรงพยาบาลของนาโนเทคโนโลยี ส่วนต้นทุนมหาศาลที่ใช้ในวันนั้น มาจากมหาเศรษฐีผู้ร่วมก่อตั้ง Google อย่าง Sergey Brin ที่เห็นว่ามันอาจเป็นคำตอบของปัญหาอาหารโลกในอนาคต
แต่เรื่องนี้มีอะไรมากกว่าที่สื่อกระแสหลักอยากให้คุณรู้
หลังจากเปิดตัวเนื้อในห้องแล็บ โลกก็เหมือนถูกปลุกให้ตื่นขึ้นในอีกมิติหนึ่ง บริษัทสตาร์ทอัพที่เคยเน้นเขียนโค้ด เริ่มหันมาเขียนสูตรเนื้อ บริษัทรายใหญ่อย่าง Cargill, Tyson Foods และแม้แต่ Richard Branson ก็เทเงินสนับสนุนบริษัทรุ่นใหม่อย่าง Mosa Meat ซึ่งก่อตั้งโดย Dr. Post เองในปี 2016 พร้อมแผนทะเยอทะยานที่จะส่ง “เนื้อจากแล็บ” เข้าซูเปอร์มาร์เก็ตภายในทศวรรษเดียว
Mosa Meat พยายามลดต้นทุนจากหลักแสน ให้เหลือหลักร้อย และวันนี้บริษัทเหล่านี้กำลังสร้างโรงงานที่ผลิตเนื้อในถังหมักขนาดยักษ์ ไม่ต่างจากโรงเบียร์ พวกเขาเลี้ยงเซลล์วัวในน้ำเลี้ยงที่เดิมทีเคยใช้เซรุ่มจากลูกวัว (Fetal Bovine Serum) ซึ่งเป็นสิ่งที่ย้อนแย้ง ที่สวนทางกับภาพ “ปลอดภัยไร้เลือด” มาก เพราะในขณะที่โฆษณาว่า “ปลอดการฆ่า” แต่กลับใช้ส่วนผสมที่ได้มาจากเลือดลูกวัวที่ยังไม่เกิด จนต้องหาทางเปลี่ยนสูตรเป็น “น้ำเลี้ยงเทียม” ที่มาจากสารเคมีและอาหารสังเคราะห์แทน
ด้วยโครงสร้าง scaffold ที่ช่วยให้เซลล์ก่อตัวเป็นเนื้อเยื่อ และ กระบวนการเพาะเลี้ยงใน bioreactor ขนาดยักษ์ ที่เปลี่ยนเซลล์เล็ก ๆ ให้เป็นเนื้อก้อนใหญ่ในเวลาไม่กี่สัปดาห์
แต่ขณะที่ภาพความล้ำซึ่งดูจะเติบโตอย่างสดใส กลับมีเงามืดที่เติบโตพร้อมกันไปเงียบๆไม่ต่างกับอนาคินและดาร์ธเวเดอร์
แม้จะเป็นนวัตกรรมล้ำหน้า แต่ทุกขั้นตอนถูกห่อหุ้มไว้ด้วย “สิทธิบัตร” สิ่งที่ทำให้เนื้อชนิดนี้ไม่ได้เป็นของทุกคน แต่เป็นสมบัติทางปัญญาของบริษัทเท่านั้น เนื้อจากเซลล์เหล่านี้ ไม่เหมือนเนื้อจากฟาร์มที่ใครก็เลี้ยงเองได้ ไม่สามารถเก็บเมล็ดพันธุ์ไว้เพาะรุ่นหน้าแบบชาวนาในอดีต ทุกอย่างต้องเริ่มต้นในห้องแล็บ ต้องใช้เทคโนโลยีเฉพาะ ต้องมีสูตรลับเฉพาะ ต้องพึ่งบริษัทที่มีสิทธิบัตรครอบครองชีวิตเซลล์เพียงไม่กี่เจ้า
Mosa Meat ไม่ได้หยุดแค่การผลิต พวกเขายื่นจด สิทธิบัตรกว่า 10 กลุ่ม ครอบคลุมตั้งแต่สูตรน้ำเลี้ยง วิธีเพาะเลี้ยงเซลล์ ไปจนถึงวิธีห่อบรรจุสินค้าขั้นสุดท้าย กล่าวอีกอย่างคือ ถ้าใครอยากทำเนื้อเพาะเลี้ยงแบบนี้บ้าง ก็ต้อง “จ่ายค่าลิขสิทธิ์” ให้เขาเสียก่อน เรากำลังก้าวสู่ยุคที่ อาหารไม่ใช่ผลผลิตจากดินและแรงคน แต่เป็นผลผลิตของทรัพย์สินทางปัญญา และเมื่อใดที่ “เนื้อ” กลายเป็นสิ่งที่คนผลิตเองไม่ได้ ต้องซื้อจากห้างเท่านั้น เกษตรกรกลายเป็นผู้บริโภค ผู้บริโภคกลายเป็นผู้ขึ้นอยู่กับระบบ ห่วงโซ่อาหารที่เคยเป็นของชุมชนถูกตัดขาดด้วยท่อส่งจากห้องทดลองสู่จานอาหาร เราไม่ได้ซื้อเนื้อ แต่ “เช่าเทคโนโลยี” ที่ผลิตเนื้อมาให้เรากิน
และที่น่าสนใจคือ รัฐบาลในหลายประเทศกลับเป็นผู้ให้ทุนสนับสนุน เช่น โครงการของสหภาพยุโรปที่มอบเงินกว่า 2 ล้านยูโรให้ Dr. Post และ Mosa Meat รวมถึงโครงการของสิงคโปร์ที่ให้ใบอนุญาตจำหน่ายเนื้อเพาะเลี้ยงรายแรกของโลกในปี 2020 ราวกับว่า “เนื้อจากแล็บ” กำลังจะกลายเป็นนโยบายด้านความมั่นคงอาหารแห่งอนาคต
มันไม่ใช่เรื่องของการวิจัยอีกต่อไป แต่มันคือการปูทางอำนาจใหม่ ที่เปลี่ยน “อาหาร” ให้กลายเป็น “ซอฟต์แวร์ชีวภาพ” ที่จดทะเบียนครอบครองสิทธิ์แบบเดียวกับแอปในมือถือ
แล้วการใช้สื่อก็จะมาในรุปแบบที่ประชาชนโห่ร้องดีใจ เฉลิมฉลองการเกิดขึ้นของมันโดยไม่รู้สึกว่า เสรีภาพในการจัดการด้านอาหารสิ้นสุดลงแล้ว ในทางหนึ่ง มันอาจดูสวยงามไร้ที่ติ ช่วยลดการฆ่าสัตว์ ลดการปล่อยก๊าซเรือนกระจก และให้โปรตีนสะอาดแก่คนจำนวนมาก
แต่อีกทางหนึ่ง มันคือการรวมศูนย์อำนาจด้านอาหารไว้ในมือบริษัทยักษ์ใหญ่ ที่สามารถตั้งราคาตามใจ และควบคุมทุกขั้นตอนตั้งแต่ฟาร์ม (ในหลอดทดลอง) ถึงโต๊ะอาหารของเรา
เกษตรกรจะหมดบทบาท เพราะไม่มีใครต้องเลี้ยงสัตว์อีก ผู้บริโภคจะหมดทางเลือก เพราะสูตรทุกอย่างถูกจดสิทธิบัตร สุดท้าย คนธรรมดาอย่างเราอาจ “มีเงินก็ยังไม่มีสิทธิ์ทำอาหารกินเอง”
ไม่มีใครในหมู่บ้านจะต้มแกงจากวัตถุดิบแล็บเหล่านี้ได้โดยไม่จ่ายค่าลิขสิทธิ์ ไม่มีใครปลูกหรือเพาะเนื้อได้เอง เพราะเขาถือสิทธิบัตร ไม่มีใครรู้ส่วนผสมที่แท้จริง เพราะมันคือ “ความลับทางการค้า”
หลายๆคนเริ่มคิดในใจว่า…นี่ไม่ใช่เรื่องเล็กอีกต่อไป เพราะนี่อาจไม่ใช่แค่เนื้อจากห้องแล็บ แต่ มันคือจุดเริ่มต้นของอนาคตของอาหารที่ไม่เป็นของประชาชนอีกต่อไป มันคือการเริ่มต้นของยุคที่มนุษย์จะไม่สามารถ “เข้าครัวของตัวเอง” ได้อีกต่อไป
ไหนๆเราตามมาถึงตอนนี้แล้ว เข้าหมวดที่ 2 ของอาหารอนาคตแล้ว เฮียไม่ได้บอกว่าเทคโนโลยีไม่ดีนะครับ เราตัดสินเดี๋ยวนี้ไม่ได้ แต่เรารู้เรื่องของมันได้
แต่โลกนี้เต็มไปด้วยคำว่า “ดีต่อโลก” ที่ซ่อนคำว่า “ดีต่อผู้ถือหุ้น” อยู่ข้างใน เราอาจจะกำลังก้าวสู่ยุคที่ “เนื้อไม่ได้ปลอดภัยขึ้น แต่ถูกควบคุมง่ายขึ้น” และประชาชนก็อาจกลายเป็นเพียง “ผู้ใช้บริการเนื้อ” ที่ไม่มีสิทธิ์แม้แต่จะรู้ว่าเนื้อในจานคืออะไรบ้างแน่
โลกอาหารในอนาคตไม่ได้ขึ้นกับว่าเราปลูกอะไร แต่ขึ้นกับว่า “ใครจดสิทธิบัตรก่อน” และเมื่อถึงวันนั้น เฮียแอบคิดว่า เราอาจไม่ได้เสียแค่ฟาร์มและครัว แต่เรากำลังเสีย “เสรีภาพในการกิน” ไปอย่างช้า ๆ ด้วยรอยยิ้มของนักลงทุนและเสียบปรบมือจาก "ใครบางคน"
ทุกวันนี้ใครนิยมไดเอทอะไร ภูมิใจในการดูแลสุขภาพยังไง ก็ทำไปเหอะครับ ขอเพียงว่า เส้นทางที่เดินอยู่นั้น สนับสนุนเกษตกร สนับสนุน local ให้แข็งแรง ทุกสังคมมีทั้งคนดีและคนไม่ดี เราค่อยๆ verify สนับสนุนคนดีๆ แต่ไม่ใช่ไปเดียจฉันท์ลงโทษคนไม่ดี เราเสริมความรู้ให้เขา พยายามโอบอุ้มพวกเขา ถ้าชีวิตดีขึ้น การออมเห็นผลขึ้น อาจทำให้ชีวิตทุกคนดีขึ้น
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 812cff5a:5c40aeeb
2025-05-28 01:13:02
@ 812cff5a:5c40aeeb
2025-05-28 01:13:02ميزة حسابات Nostr: حرية مطلقة دون تقديم معلومات شخصية
في عصرٍ تسيطر فيه شركات التكنولوجيا الكبرى على بيانات المستخدمين، تأتي شبكة Nostr كحل جذري يعيد للمستخدم السيطرة على هويته الرقمية. واحدة من أبرز ميزات Nostr هي القدرة على إنشاء عدد غير محدود من الحسابات، دون الحاجة لتقديم أي معلومات شخصية، مثل رقم الهاتف أو البريد الإلكتروني.
مفاتيح بدل الحسابات
في Nostr، لا يوجد مفهوم "الحساب" التقليدي. بدلاً من ذلك، يتم إنشاء هوية المستخدم عبر زوج من المفاتيح: مفتاح خاص (Private Key) ومفتاح عام (Public Key). المفتاح العام يُستخدم لتعريفك ونشر مشاركاتك، بينما المفتاح الخاص يُستخدم لتوقيع تلك المشاركات وإثبات ملكيتك لها.
قابلية التنقل بين التطبيقات
الميزة الكبرى في هذا النموذج هي أن هذه المفاتيح يمكن استخدامها في أي تطبيق Nostr. سواء كنت تستخدم تطبيق Damus، أو Amethyst، أو أي عميل آخر، يمكنك استخدام نفس المفتاح العام للوصول إلى هويتك، منشوراتك، وقائمة متابعيك، بدون الحاجة لإعادة تسجيل أو إعادة بناء ملفك الشخصي في كل تطبيق.
لا تسجيل دخول، لا مركزية
بخلاف الشبكات الاجتماعية التقليدية التي تعتمد على تسجيل الدخول المركزي وكلمة مرور، فإن Nostr مبني على بروتوكول لا مركزي لا يحتاج إلى خوادم مركزية أو عمليات تسجيل دخول. هذا يعني أنك تتحكم بالكامل في بياناتك، ولا يمكن لأي جهة منعك أو حذف حسابك.
المرونة والخصوصية
- يمكنك إنشاء عدة مفاتيح لهويات مختلفة، كل منها تمثل شخصية مختلفة أو اهتمامًا معينًا.
- لا أحد يستطيع ربط هذه الحسابات ببعض أو تتبعها إلا إذا قمت أنت بذلك.
- يمكنك التخلي عن مفتاح واستبداله بآخر متى شئت، بدون طلب إذن من أي منصة.
خاتمة
ما يميز Nostr حقًا ليس فقط حريته التقنية، بل فلسفته المبنية على الخصوصية والتمكين. هو ليس مجرد بديل لتويتر أو فيسبوك، بل هو إطار جديد للتواصل الاجتماعي حيث الهوية تنبع من المستخدم، لا من المنصة.
-
 @ b7274d28:c99628cb
2025-05-28 01:11:43
@ b7274d28:c99628cb
2025-05-28 01:11:43In this second installment of The Android Elite Setup tutorial series, we will cover installing the nostr:npub10r8xl2njyepcw2zwv3a6dyufj4e4ajx86hz6v4ehu4gnpupxxp7stjt2p8 on your #Android device and browsing for apps you may be interested in trying out.
Since the #Zapstore is a direct competitor to the Google Play Store, you're not going to be able to find and install it from there like you may be used to with other apps. Instead, you will need to install it directly from the developer's GitHub page. This is not a complicated process, but it is outside the normal flow of searching on the Play Store, tapping install, and you're done.
Installation
From any web browser on your Android phone, navigate to the Zapstore GitHub Releases page and the most recent version will be listed at the top of the page. The .apk file for you to download and install will be listed in the "Assets."
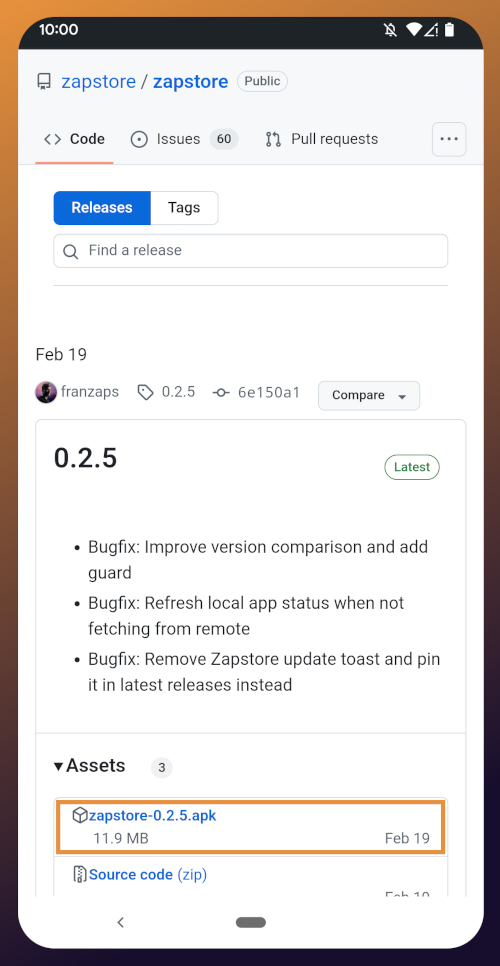
Tap the .apk to download it, and you should get a notification when the download has completed, with a prompt to open the file.
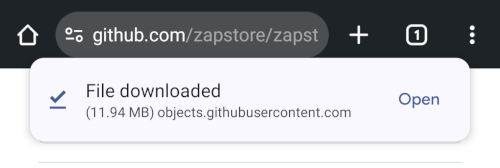
You will likely be presented with a prompt warning you that your phone currently isn't allowed to install applications from "unknown sources." Anywhere other than the Play Store is considered an "unknown source" by default. However, you can manually allow installation from unknown sources in the settings, which the prompt gives you the option to do.
In the settings page that opens, toggle it to allow installation from this source, and you should be prompted to install the application. If you aren't, simply go to your web browser's downloads and tap on the .apk file again, or go into your file browser app and you should find the .apk in your Downloads folder.
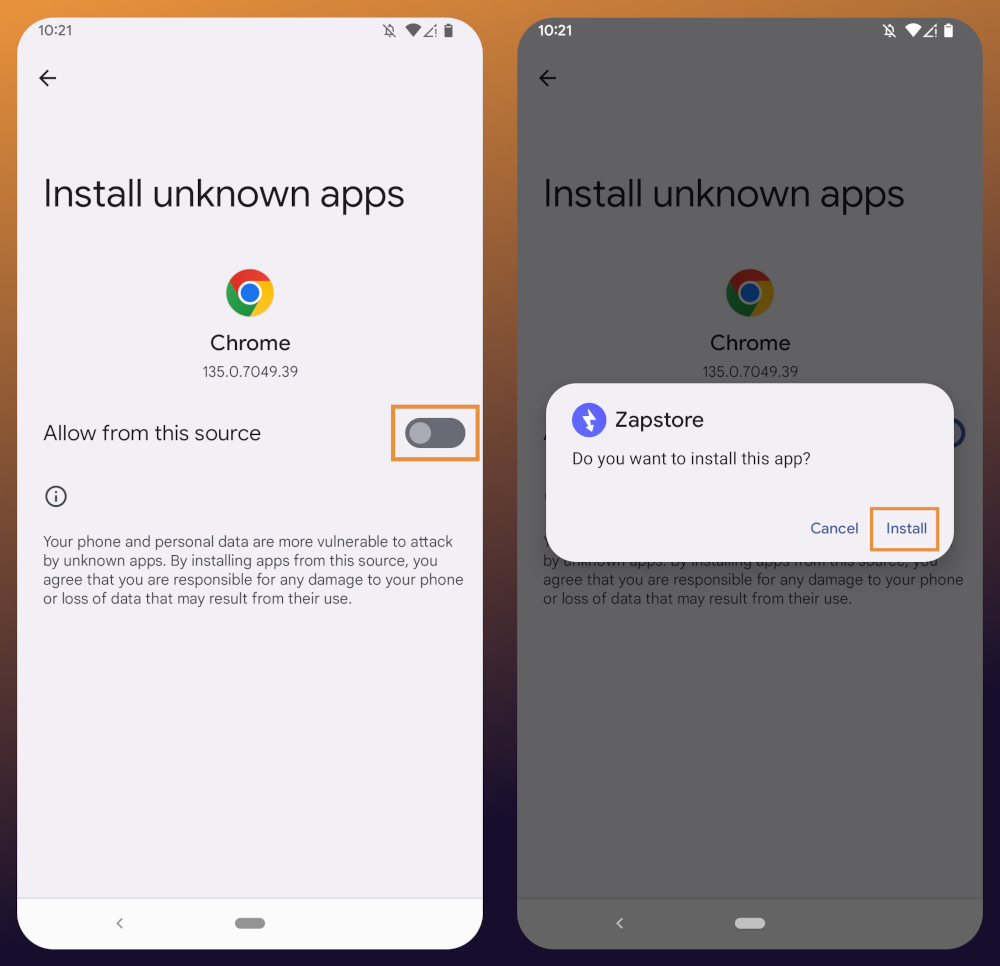
If the application doesn't open automatically after install, you will find it in your app drawer.
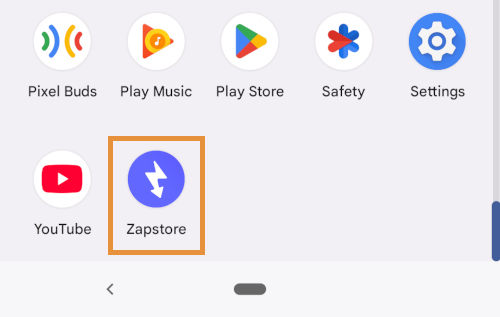
Home Page
Right at the top of the home page in the Zapstore is the search bar. You can use it to find a specific app you know is available in the Zapstore.
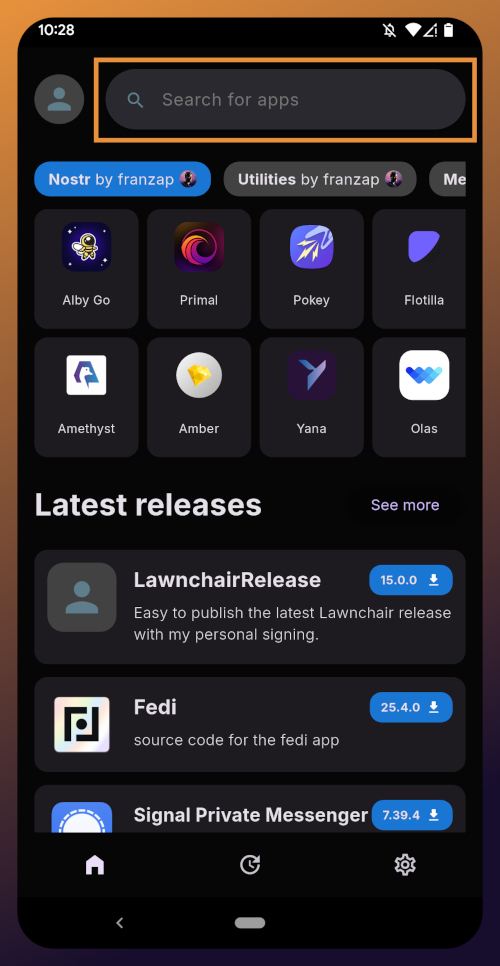
There are quite a lot of open source apps available, and more being added all the time. Most are added by the Zapstore developer, nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9, but some are added by the app developers themselves, especially Nostr apps. All of the applications we will be installing through the Zapstore have been added by their developers and are cryptographically signed, so you know that what you download is what the developer actually released.
The next section is for app discovery. There are curated app collections to peruse for ideas about what you may want to install. As you can see, all of the other apps we will be installing are listed in nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9's "Nostr" collection.
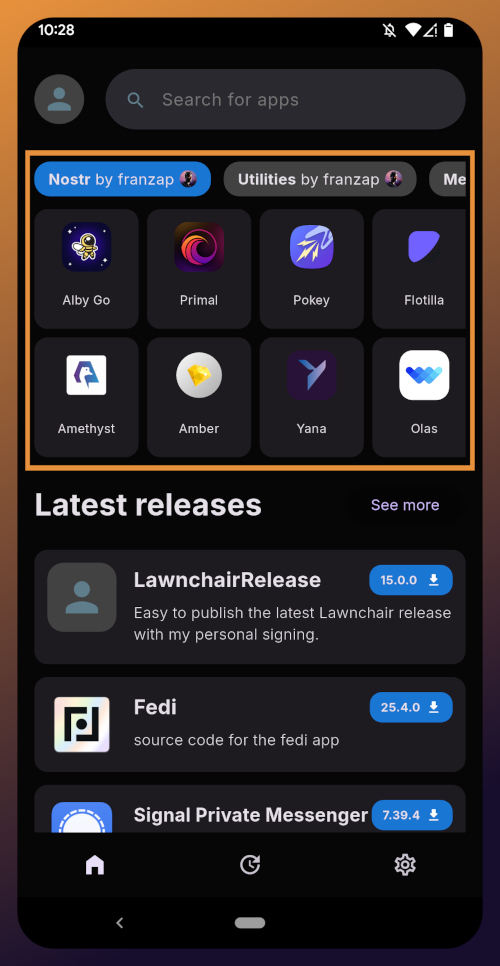
In future releases of the Zapstore, users will be able to create their own app collections.
The last section of the home page is a chronological list of the latest releases. This includes both new apps added to the Zapstore and recently updated apps. The list of recent releases on its own can be a great resource for discovering apps you may not have heard of before.
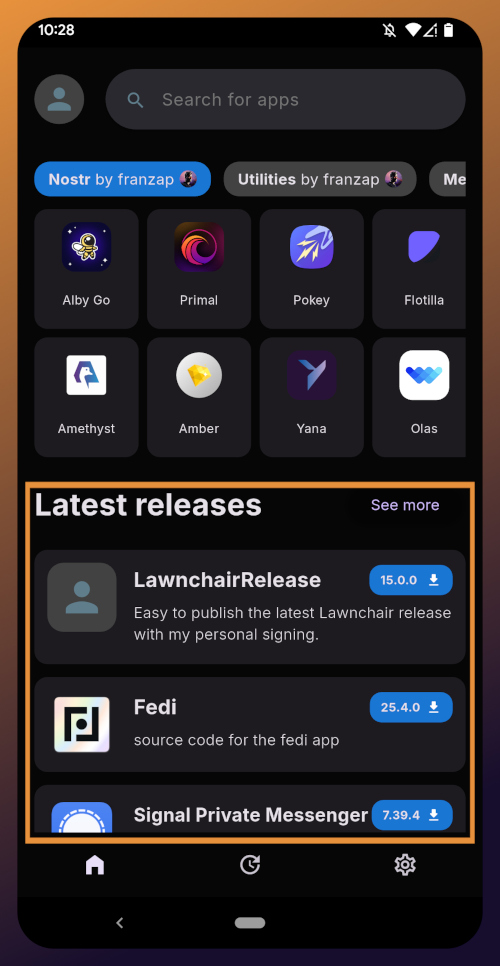
Installed Apps
The next page of the app, accessed by the icon in the bottom-center of the screen that looks like a clock with an arrow circling it, shows all apps you have installed that are available in the Zapstore. It's also where you will find apps you have previously installed that are ready to be updated. This page is pretty sparse on my test profile, since I only have the Zapstore itself installed, so here is a look at it on my main profile:
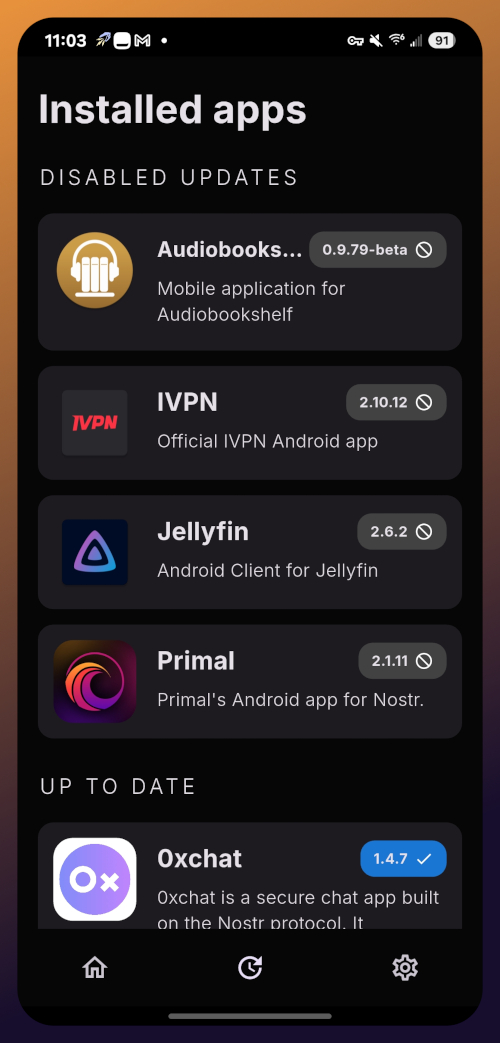
The "Disabled Apps" at the top are usually applications that were installed via the Play Store or some other means, but are also available in the Zapstore. You may be surprised to see that some of the apps you already have installed on your device are also available on the Zapstore. However, to manage their updates though the Zapstore, you would need to uninstall the app and reinstall it from the Zapstore instead. I only recommend doing this for applications that are added to the Zapstore by their developers, or you may encounter a significant delay between a new update being released for the app and when that update is available on the Zapstore.
Tap on one of your apps in the list to see whether the app is added by the developer, or by the Zapstore. This takes you to the application's page, and you may see a warning at the top if the app was not installed through the Zapstore.
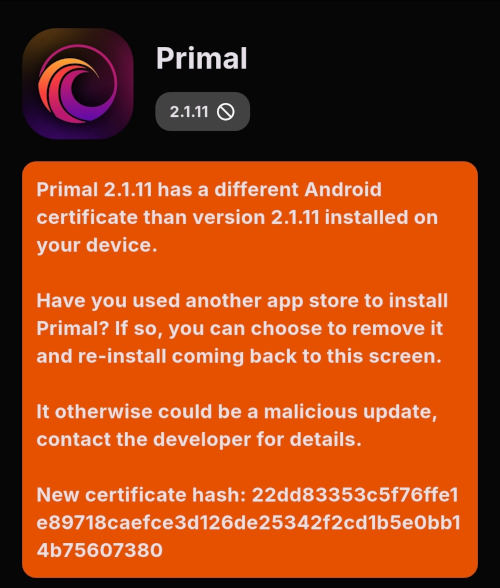
Scroll down the page a bit and you will see who signed the release that is available on the Zapstore.
In the case of Primal, even though the developer is on Nostr, they are not signing their own releases to the Zapstore yet. This means there will likely be a delay between Primal releasing an update and that update being available on the Zapstore.
Settings
The last page of the app is the settings page, found by tapping the cog at the bottom right.
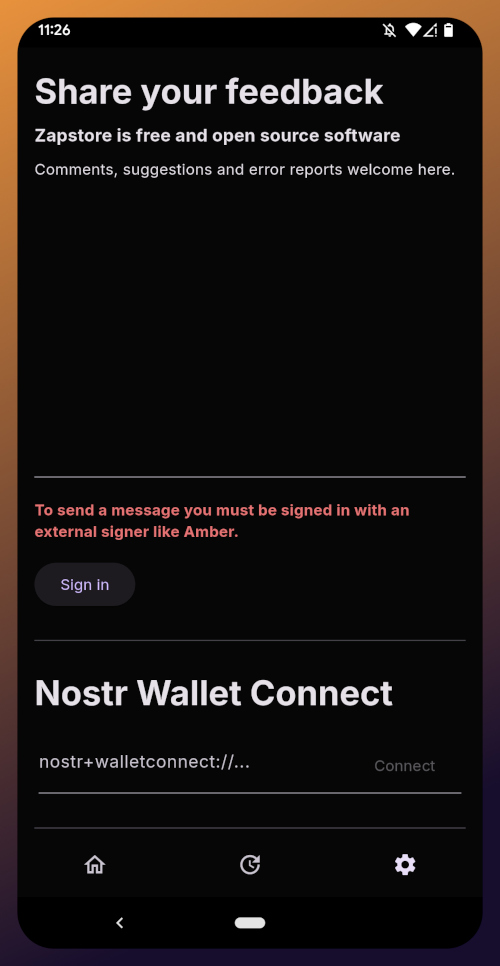
Here you can send the Zapstore developer feedback directly (if you are logged in), connect a Lightning wallet using Nostr Wallet Connect, delete your local cache, and view some system information.
We will be adding a connection to our nostr:npub1h2qfjpnxau9k7ja9qkf50043xfpfy8j5v60xsqryef64y44puwnq28w8ch wallet in part 5 of this tutorial series.
For the time being, we are all set with the Zapstore and ready for the next stage of our journey.
Continue to Part 3: Amber Signer. Nostr link: nostr:naddr1qqxnzde5xuengdeexcmnvv3eqgstwf6d9r37nqalwgxmfd9p9gclt3l0yc3jp5zuyhkfqjy6extz3jcrqsqqqa28qy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qg6waehxw309aex2mrp0yhxyunfva58gcn0d36zumn9wss80nug
-
 @ a012dc82:6458a70d
2024-12-30 05:51:11
@ a012dc82:6458a70d
2024-12-30 05:51:11Table Of Content
-
The Influence of Global Oil Prices
-
Bitcoin's Roller Coaster Ride
-
Anticipation Surrounding the 2024 Halving Event
-
The Broader Crypto Landscape
-
Conclusions
-
FAQ
In the ever-evolving world of cryptocurrencies, Bitcoin stands as a beacon, often dictating the mood of the entire crypto market. Its price fluctuations are closely watched by investors, analysts, and enthusiasts alike. Max Keiser, a prominent figure in the crypto space, recently shed light on some intriguing factors that might be influencing Bitcoin's current price trajectory. This article delves into Keiser's insights, exploring the broader implications of global events on Bitcoin's market performance.
The Influence of Global Oil Prices
Max Keiser, a renowned Bitcoin advocate and former trader, recently drew attention to the interplay between global oil prices and Bitcoin's market performance. Responding to a post by German economics expert, Holger Zschaepitz, Keiser highlighted the significance of Brent oil reaching $90 per barrel for the first time since the previous November. According to Keiser, the surge in oil prices, driven by Saudi Arabia's decision to extend its reduction in oil production for another three months, has had ripple effects in the financial world. One of these effects is the shift of investor interest towards higher interest deposit USD accounts. This diversion of investments is creating what Keiser terms as "a small headwind for Bitcoin," implying that as traditional markets like oil show promise, some investors might be reconsidering their cryptocurrency positions.
Bitcoin's Roller Coaster Ride
The cryptocurrency market, known for its volatility, witnessed Bitcoin's price undergoing significant fluctuations recently. A notable event that gave Bitcoin a temporary boost was Grayscale's triumph over the SEC in a legal battle concerning the conversion of its Bitcoin Trust into a spot ETF. This victory led to a rapid 7.88% spike in Bitcoin's price within a mere hour, pushing it from the $26,000 bracket to briefly touch the $28,000 threshold. However, this euphoria was short-lived. Over the subsequent week, the cryptocurrency saw its gains erode, settling in the $25,400 range. At the time the reference article was penned, Bitcoin was hovering around $25,688.
Anticipation Surrounding the 2024 Halving Event
The Bitcoin community is abuzz with anticipation for the next scheduled Bitcoin halving, projected to take place in April-May 2024. This event will see the rewards for Bitcoin miners being slashed by half, resulting in a decreased supply of Bitcoin entering the market. Historically, such halvings have acted as catalysts, propelling Bitcoin's price upwards. A case in point is the aftermath of the 2020 halving, post which Bitcoin soared to an all-time high of $69,000 in October 2021. However, some financial analysts argue that this surge was less about the halving and more a consequence of the extensive monetary measures adopted by institutions like the US Federal Reserve. These measures, taken in response to the pandemic and the ensuing lockdowns, flooded the market with cash, potentially driving up Bitcoin's price.
The Broader Crypto Landscape
While Bitcoin remains the most dominant and influential cryptocurrency, it's essential to consider its position within the broader crypto ecosystem. Other cryptocurrencies, often referred to as 'altcoins', also play a role in shaping investor sentiment and market dynamics. Factors such as technological advancements, regulatory changes, and global economic shifts not only impact Bitcoin but the entire crypto market. As investors diversify their portfolios and explore newer blockchain projects, Bitcoin's role as the market leader is continually tested. Yet, its pioneering status and proven resilience make it a focal point of discussions and analyses in the crypto world.
Conclusion
Bitcoin, the flagship cryptocurrency, has always been subject to a myriad of market forces and global events. While its inherent potential remains undeniable, the current market landscape, shaped by factors ranging from oil prices to global economic policies, presents challenges. Yet, with events like the 2024 halving on the horizon, there's an air of optimism among Bitcoin enthusiasts and investors about the future trajectory of this digital asset.
FAQ
Who is Max Keiser? Max Keiser is a prominent Bitcoin advocate, former trader, and well-known crypto podcaster.
What did Keiser say about Bitcoin's price? Keiser pointed out that rising global oil prices and the allure of higher interest deposit USD accounts are creating a "small headwind" for Bitcoin.
How did Grayscale's legal victory affect Bitcoin? Grayscale's win over the SEC led to a 7.88% spike in Bitcoin's price within an hour.
When is the next Bitcoin halving expected? The next Bitcoin halving is projected to occur around April-May 2024.
Did the 2020 Bitcoin halving influence its price? Yes, post the 2020 halving, Bitcoin reached an all-time high of $69,000 in October 2021.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ b7274d28:c99628cb
2025-05-28 00:59:49
@ b7274d28:c99628cb
2025-05-28 00:59:49Your identity is important to you, right? While impersonation can be seen in some senses as a form of flattery, we all would prefer to be the only person capable of representing ourselves online, unless we intentionally delegate that privilege to someone else and maintain the ability to revoke it.
Amber does all of that for you in the context of #Nostr. It minimizes the possibility of your private key being compromized by acting as the only app with access to it, while all other Nostr apps send requests to Amber when they need something signed. This even allows you to give someone temporary authority to post as you without giving them your private key, and you retain the authority to revoke their permissions at any time.
nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 has provided Android users with an incredibly powerful tool in Amber, and he continues to improve its functionality and ease of use. Indeed, there is not currently a comparative app available for iOS users. For the time being, this superpower is exclusive to Android.
Installation
Open up the Zapstore app that you installed in the previous stage of this tutorial series.
Very likely, Amber will be listed in the app collection section of the home page. If it is not, just search for "Amber" in the search bar.
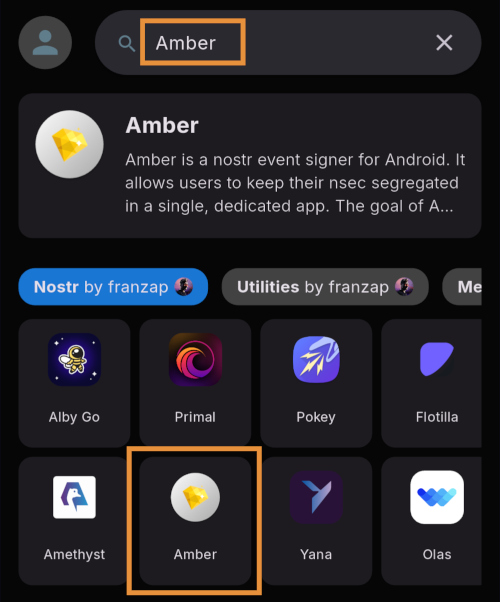
Opening the app's page in the Zapstore shows that the release is signed by the developer. You can also see who has added this app to one of their collections and who has supported this app with sats by zapping the release.
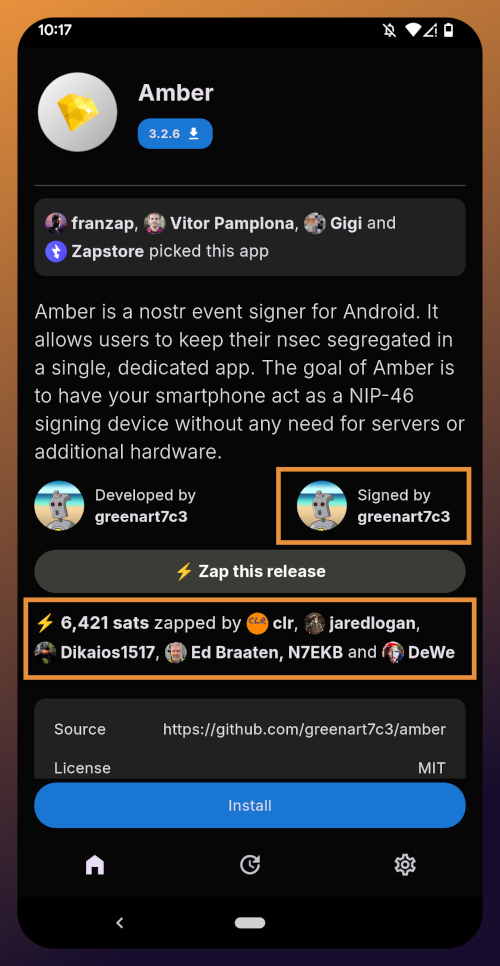
Tap "Install" and you will be prompted to confirm you are sure you want to install Amber.
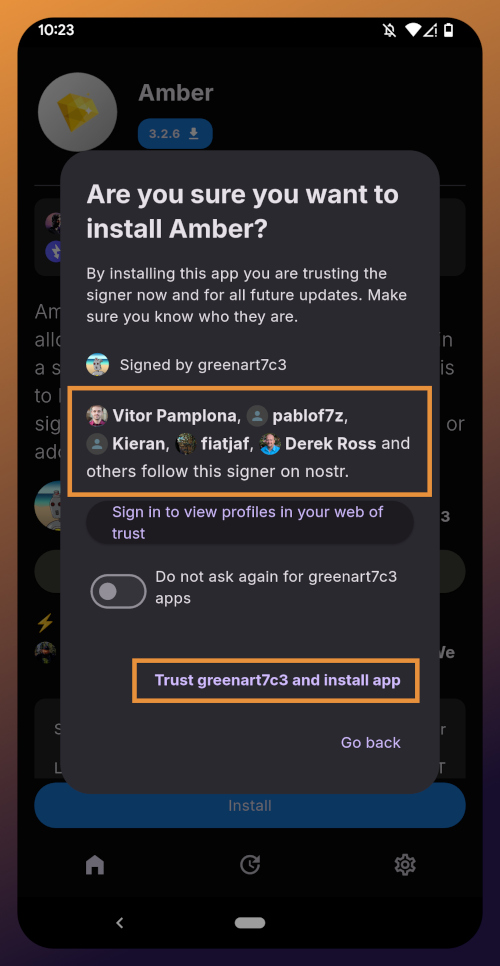
Helpfully, you are informed that several other users follow this developer on Nostr. If you have been on Nostr a while, you will likely recognize these gentlemen as other Nostr developers, one of them being the original creator of the protocol.
You can choose to never have Zapstore ask for confirmation again with apps developed by nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5, and since we have another of his apps to install later in this tutorial series, I recommend you toggle this on. Then tap on "Trust greenart7c3 and install app."
Just like when you installed the Zapstore from their GitHub, you will be prompted to allow the Zapstore to install apps, since Android considers it an "unknown source."
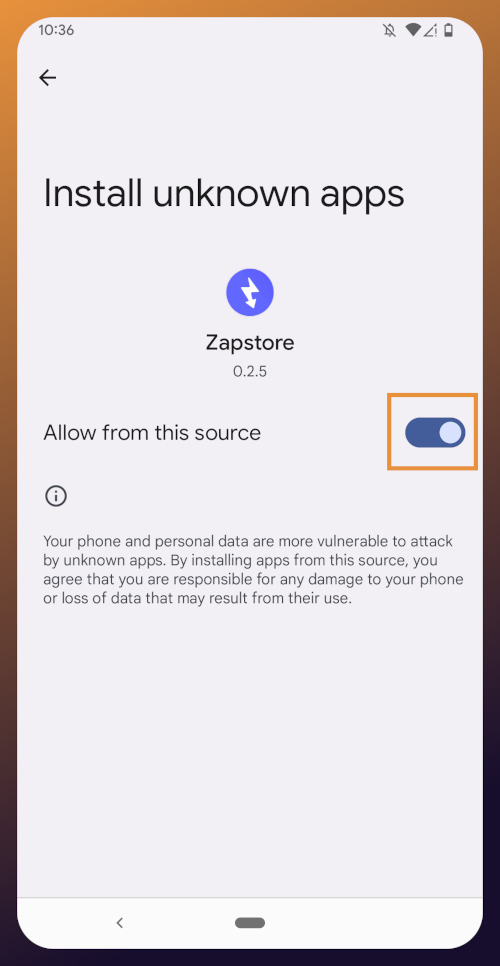
Once you toggle this on and use the back button to get back to the Zapstore, Amber will begin downloading and then present a prompt to install the app. Once installed, you will see a prompt that installation was a success and you can now open the app.
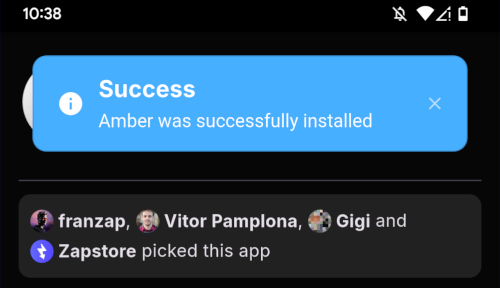
From here, how you proceed will depend on whether you need to set up a new Nostr identity or use Amber with an existing private key you already have set up. The next section will cover setting up a new Nostr identity with Amber. Skip to the section titled "Existing Nostrich" if you already have an nsec that you would like to use with Amber.
New Nostrich
Upon opening the application, you will be presented with the option to use an existing private key or create a new Nostr account. Nostr doesn't really have "accounts" in the traditional sense of the term. Accounts are a relic of permissioned systems. What you have on Nostr are keys, but Amber uses the "account" term because it is a more familiar concept, though it is technically inaccurate.
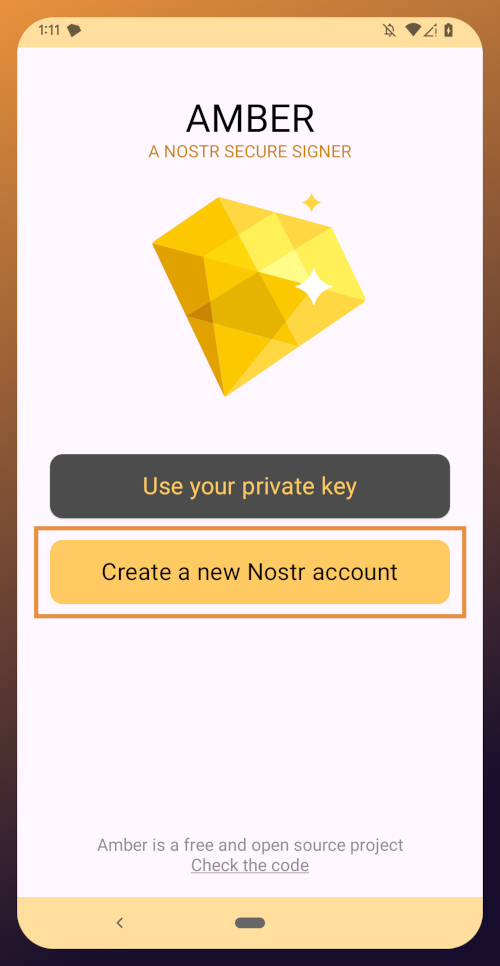
Choose "Create a new Nostr account" and you will be presented with a screen telling you that your Nostr account is ready. Yes, it was really that easy. No email, no real name, no date of birth, and no annoying capcha. Just "Create a new account" and you're done.
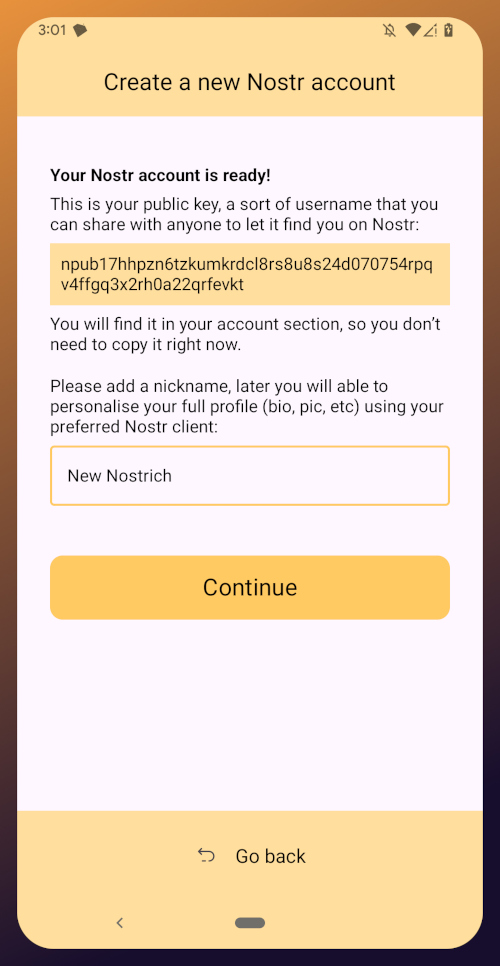
The app presents you with your public key. This is like an address that can be used to find your posts on Nostr. It is 100% unique to you, and no one else can post a note that lists this npub as the author, because they won't have the corresponding private key. You don't need to remember your npub, though. You'll be able to readily copy it from any Nostr app you use whenever you need it.
You will also be prompted to add a nickname. This is just for use within Amber, since you can set up multiple profiles within the app. You can use anything you want here, as it is just so you can tell which profile is which when switching between them in Amber.
Once you've set your nickname, tap on "Continue."
The next screen will ask you what Amber's default signing policy should be.
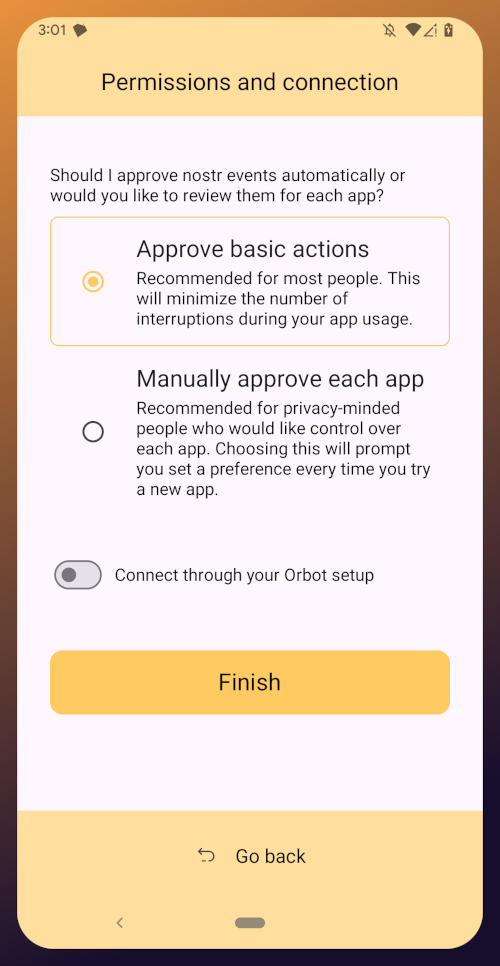
The default is to approve basic actions, referring to things that are common for Nostr clients to request a signature for, like following another user, liking a post, making a new post, or replying. If you are more concerned about what Amber might be signing for on your behalf, you can tell it to require manual approval for each app.
Once you've made your decision, tap "Finish." You will also be able to change this selection in the app settings at any time.
With this setup out of the way, you are now presented with the main "Applications" page of the app.
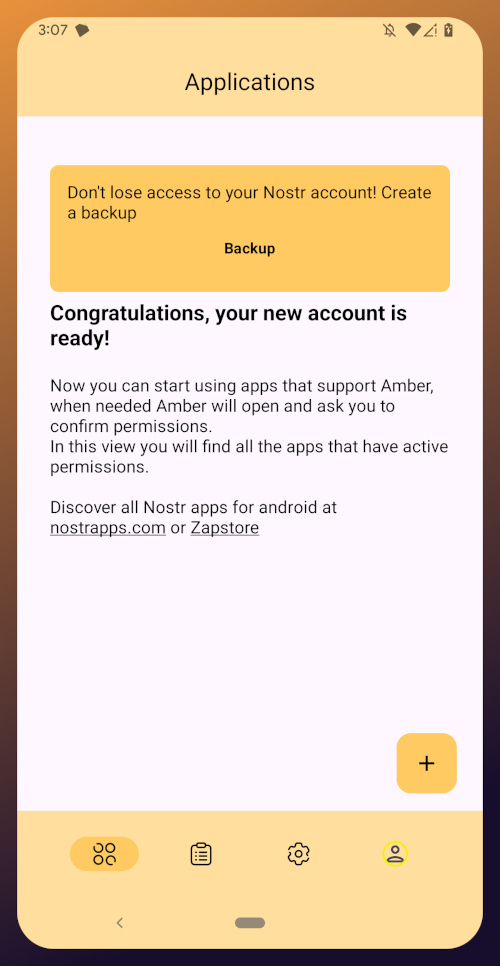
At the top, you have a notification encouraging you to create a backup. Let's get that taken care of now by tapping on the notification and skipping down to the heading titled "Backing Up Your Identity" in this tutorial.
Existing Nostrich
Upon opening the application, you will be presented with the option to use your private key or create a new Nostr account. Choose the former.
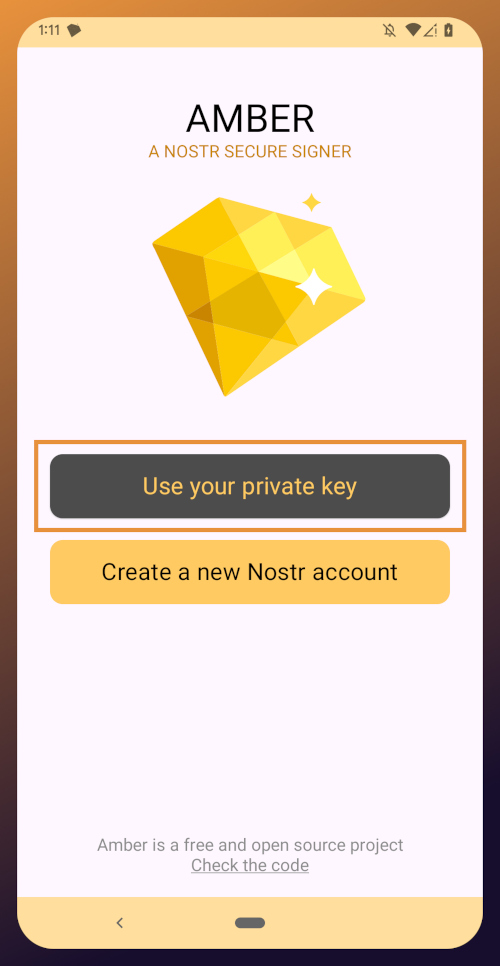
The next screen will require you to paste your private key.
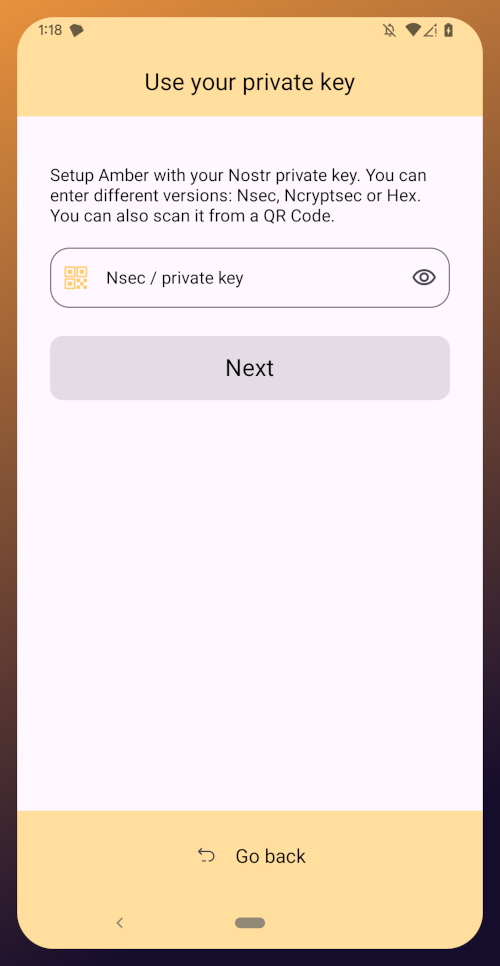
You will need to obtain this from whatever Nostr app you used to create your profile, or any other Nostr app that you pasted your nsec into in the past. Typically you can find it in the app settings and there will be a section mentioning your keys where you can copy your nsec. For instance, in Primal go to Settings > Keys > Copy private key, and on Amethyst open the side panel by tapping on your profile picture in the top-left, then Backup Keys > Copy my secret key.
After pasting your nsec into Amber, tap "Next."
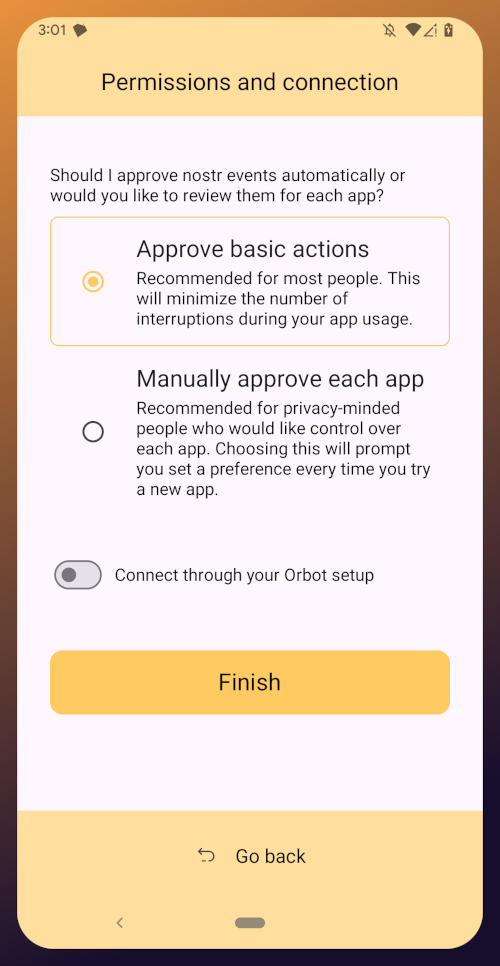
Amber will give you a couple options for a default signing policy. The default is to approve basic actions, referring to things that are common for Nostr clients to request a signature for, like following another user, liking a post, making a new post, or replying. If you are more concerned about what Amber might be signing for on your behalf, you can tell it to require manual approval for each app.
Once you've made your decision, tap "Finish." You will also be able to change this selection in the app settings at any time.
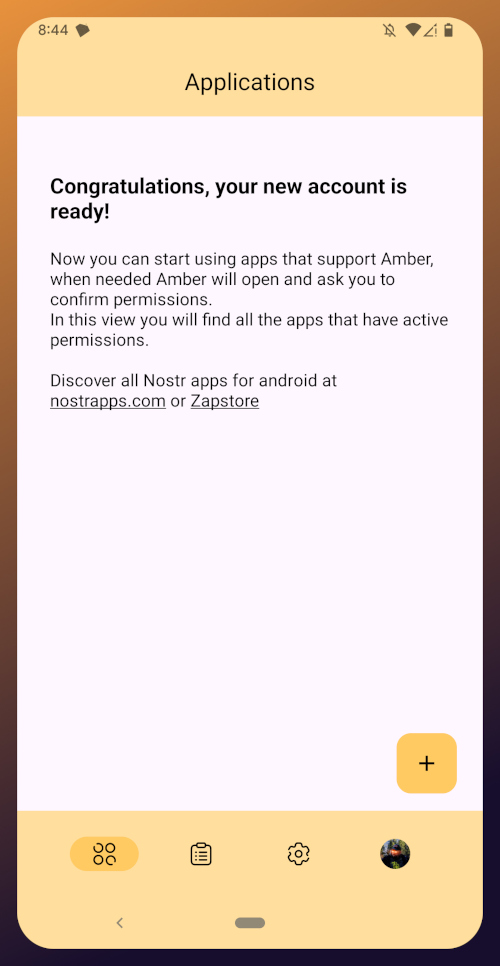
With this setup out of the way, you are now presented with the main "Applications" page of the app. You have nothing here yet, since you haven't used Amber to log into any Nostr apps, but this will be where all of the apps you have connected with Amber will be listed, in the order of the most recently used at the top.
Before we go and use Amber to log into an app, though, let's make sure we've created a backup of our private key. You pasted your nsec into Amber, so you could just save that somewhere safe, but Amber gives you a few other options as well. To find them, you'll need to tap the cog icon at the bottom of the screen to access the settings, then select "Backup Keys."
Backing Up Your Identity
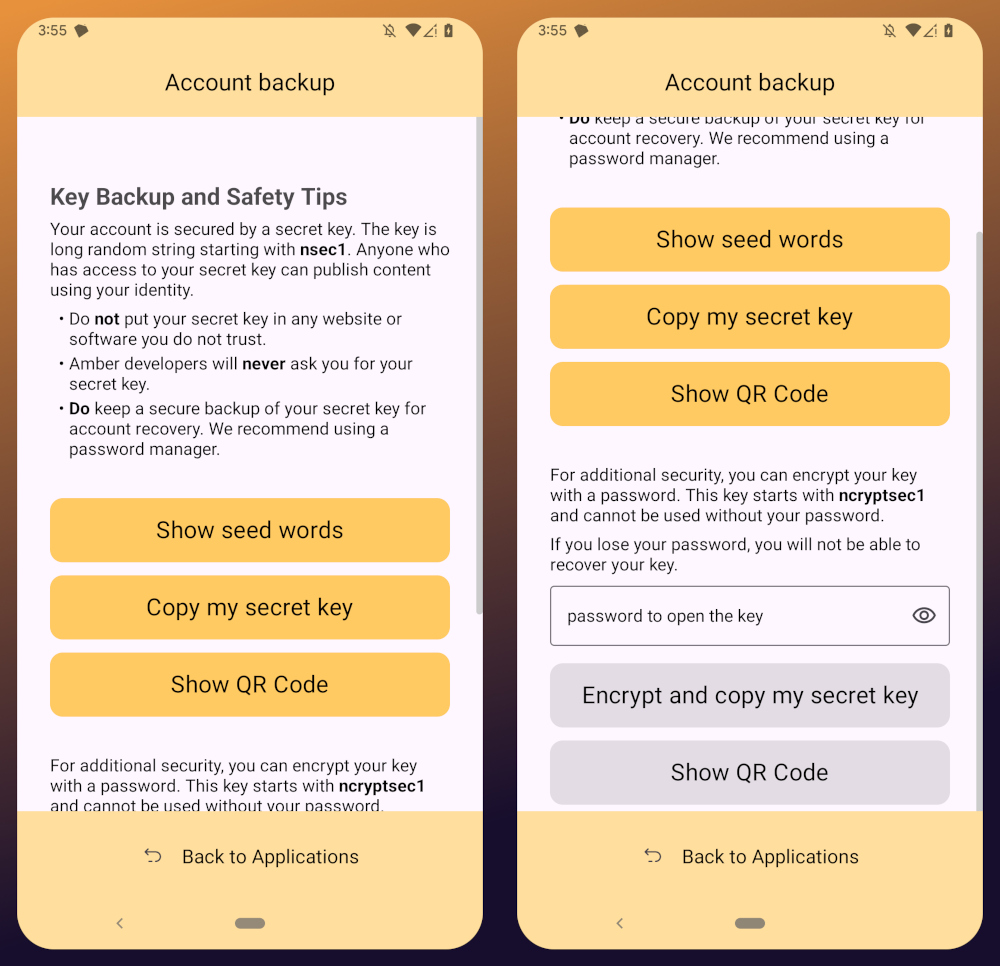
You'll notice that Amber has a few different options for backing up your private key that it can generate.
First, it can give you seed words, just like a Bitcoin seed. If you choose that option, you'll be presented with 12 words you can record somewhere safe. To recover your Nostr private key, you just have to type those words into a compatible application, such as Amber.
The next option is to just copy the secret/private key in its standard form as an "nsec." This is the least secure way to store it, but is also the most convenient, since it is simple to paste into another signer application. If you want to be able to log in on a desktop web app, the browser extension Nostr signers won't necessarily support entering your 12 word seed phrase, but they absolutely will support pasting in your nsec.
You can also display a QR code of your private key. This can be scanned by Amber signer on another device for easily transferring your private key to other devices you want to use it on. Say you have an Android tablet in addition to your phone, for instance. Just make sure you only use this function where you can be certain that no one will be able to get a photograph of that QR code. Once someone else has your nsec, there is no way to recover it. You have to start all over on Nostr. Not a big deal at this point in your journey if you just created a Nostr account, but if you have been using Nostr for a while and have built up a decent amount of reputation, it could be much more costly to start over again.
The next options are a bit more secure, because they require a password that will be used to encrypt your private key. This has some distinct advantages, and a couple disadvantages to be aware of. Using a password to encrypt your private key will give you what is called an ncryptsec, and if this is leaked somehow, whoever has it will not necessarily have access to post as you on Nostr, the way they would if your nsec had been leaked. At least, not so long as they don't also have your password. This means you can store your ncryptsec in multiple locations without much fear that it will be compromised, so long as the password you used to encrypt it was a strong and unique one, and it isn't stored in the same location. Some Nostr apps support an ncryptsec for login directly, meaning that you have the option to paste in your ncryptsec and then just log in with the password you used to encrypt it from there on out. However, now you will need to keep track of both your ncryptsec and your password, storing both of them safely and separately. Additionally, most Nostr clients and signer applications do not support using an ncryptsec, so you will need to convert it back to a standard nsec (or copy the nsec from Amber) to use those apps.
The QR option using an ncryptsec is actually quite useful, though, and I would go this route when trying to set up Amber on additional devices, since anyone possibly getting a picture of the QR code is still not going to be able to do anything with it, unless they also get the password you used to encrypt it.
All of the above options will require you to enter the PIN you set up for your device, or biometric authentication, just as an additional precaution before displaying your private key to you.
As for what "store it in a safe place" looks like, I highly recommend a self-hosted password manager, such as Vaultwarden+Bitwarden or KeePass. If you really want to get wild, you can store it on a hardware signing device, or on a steel seed plate.
Additional Settings
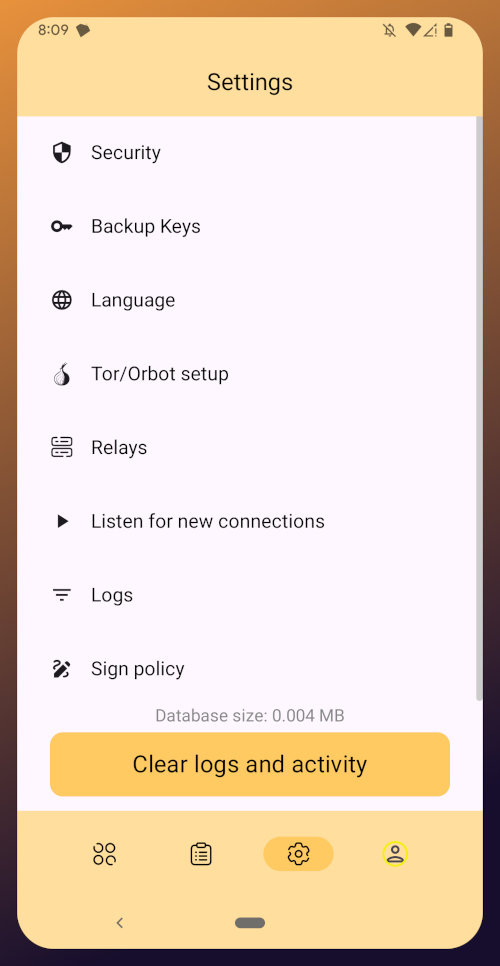
Amber has some additional settings you may want to take advantage of. First off, if you don't want just anyone who has access to your phone to be able to approve signing requests, you can go into the Security settings add a PIN or enable biometrics for signing requests. If you enable the PIN, it will be separate from the PIN you use to access your phone, so you can let someone else use your phone, like your child who is always begging to play a mobile game you have installed, without worrying that they might have access to your Nostr key to post on Amethyst.
Amber also has some relay settings. First are the "Active relays" which are used for signing requests sent to Amber remotely from Nostr web apps. This is what enables you to use Amber on your phone to log into Nostr applications on your desktop web browser, such as Jumble.social, Coracle.social, or Nostrudel.ninja, eliminating your need to use any other application to store your nsec whatsoever. You can leave this relay as the default, or you can add other relays you want to use for signing requests. Just be aware, not all relays will accept the notes that are used for Nostr signing requests, so make sure that the relay you want to use does so. In fact, Amber will make sure of this for you when you type in the relay address.
The next type of relays that you can configure in Amber are the "Default profile relays." These are used for reading your profile information. If you already had a Nostr identity that you imported to Amber, you probably noticed it loaded your profile picture and display name, setting the latter as your nickname in Amber. These relays are where Amber got that information from. The defaults are relay.nostr.band and purplepag.es. The reason for this is because they are aggregators that look for Nostr profiles that have been saved to other relays on the network and pull them in. Therefore, no matter what other relay you may save your profile to, Amber will likely be able to find it on one of those two relays as well. If you have a relay you know you will be saving your Nostr profiles to, you may want to add it to this list.
You can also set up Amber to be paired with Orbot for signing over Tor using relays that are only accessible via the Tor network. That is an advanced feature, though, and well beyond the scope of this tutorial.
Finally, you can update the default signing policy. Maybe after using Amber for a while, you've decided that the choice you made before was too strict or too lenient. You can change it to suit your needs.
Zapstore Login
Now that you are all set up with Amber, let's get you signed into your first Nostr app by going back to the Zapstore.
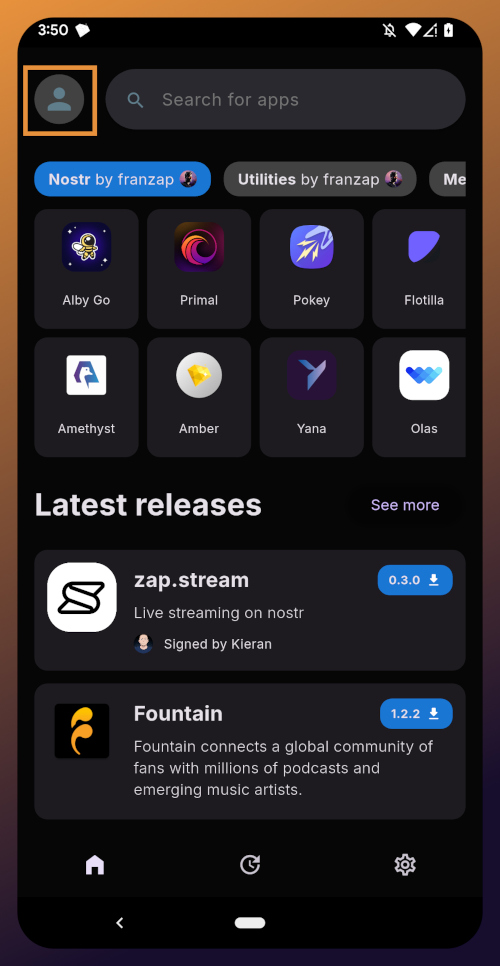
From the app's home screen, tap on the user icon in the upper left of the screen. This will open a side panel with not much on it except the option to "sign in." Go ahead and tap on it.
You will be presented with the option to either sign in with Amber, or to paste your npub. However, if you do the latter, you will only have read access, meaning you cannot zap any of the app releases. There are other features planned for the Zapstore that may also require you to be signed in with write access, so go ahead and choose to log in with Amber.
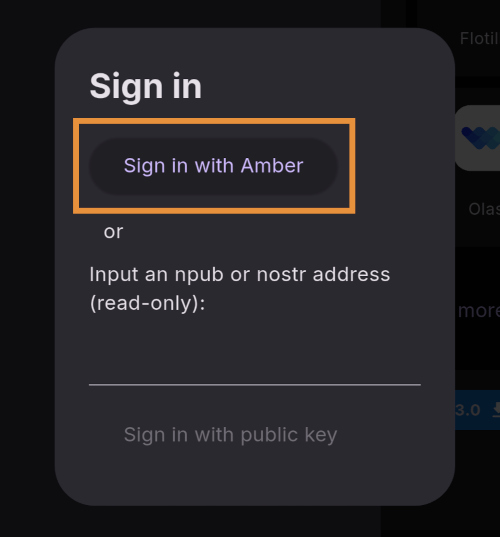
Your phone should automatically switch to Amber to approve the sign-in request.
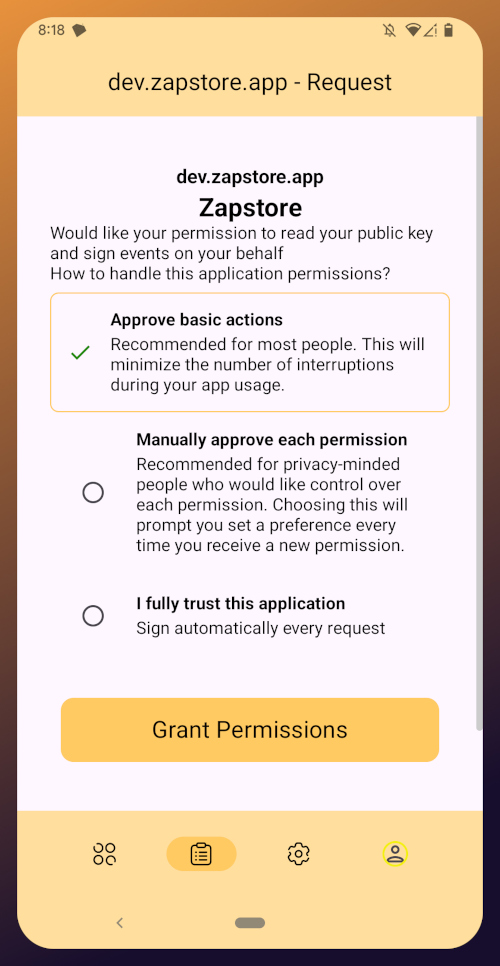
You can choose to only approve basic actions for Zapstore, require it to manually approve every time, or you can tell it that you "fully trust this application." Only choose the latter option with apps you have used for a while and they have never asked you to sign for anything suspicious. For the time being, I suggest you use the "Approve basic actions" option and tap "Grant Permissions."
Your phone will switch back to the Zapstore and will show that you are now signed in. Congratulations! From here on out, logging into most Nostr applications will be as easy as tapping on "Log in with Amber" and approving the request.
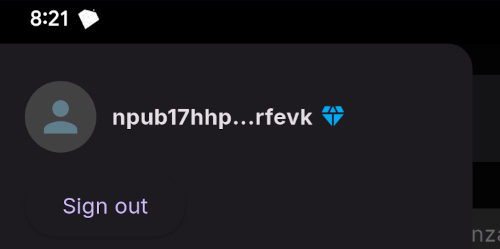
If you set up a new profile, it will just show a truncated version of your npub rather than the nickname you set up earlier. That's fine. You'll have an opportunity to update your Nostr profile in the next tutorial in this series and ensure that it is spread far and wide in the network, so the Zapstore will easily find it.
That concludes the tutorial for Amber. While we have not covered using Amber to log into Nostr web apps, that is outside the scope of this series, and I will cover it in an upcoming tutorial regarding using Amber's remote signer options in detail.
Since you're already hanging out in the Zapstore, you may as well stick around, because we will be using it right out the gate in the next part of this series: Amethyst Installation and Setup. (Coming Soon)
-
 @ 16d11430:61640947
2024-12-23 16:47:01
@ 16d11430:61640947
2024-12-23 16:47:01At the intersection of philosophy, theology, physics, biology, and finance lies a terrifying truth: the fiat monetary system, in its current form, is not just an economic framework but a silent, relentless force actively working against humanity's survival. It isn't simply a failed financial model—it is a systemic engine of destruction, both externally and within the very core of our biological existence.
The Philosophical Void of Fiat
Philosophy has long questioned the nature of value and the meaning of human existence. From Socrates to Kant, thinkers have pondered the pursuit of truth, beauty, and virtue. But in the modern age, the fiat system has hijacked this discourse. The notion of "value" in a fiat world is no longer rooted in human potential or natural resources—it is abstracted, manipulated, and controlled by central authorities with the sole purpose of perpetuating their own power. The currency is not a reflection of society’s labor or resources; it is a representation of faith in an authority that, more often than not, breaks that faith with reckless monetary policies and hidden inflation.
The fiat system has created a kind of ontological nihilism, where the idea of true value, rooted in work, creativity, and family, is replaced with speculative gambling and short-term gains. This betrayal of human purpose at the systemic level feeds into a philosophical despair: the relentless devaluation of effort, the erosion of trust, and the abandonment of shared human values. In this nihilistic economy, purpose and meaning become increasingly difficult to find, leaving millions to question the very foundation of their existence.
Theological Implications: Fiat and the Collapse of the Sacred
Religious traditions have long linked moral integrity with the stewardship of resources and the preservation of life. Fiat currency, however, corrupts these foundational beliefs. In the theological narrative of creation, humans are given dominion over the Earth, tasked with nurturing and protecting it for future generations. But the fiat system promotes the exact opposite: it commodifies everything—land, labor, and life—treating them as mere transactions on a ledger.
This disrespect for creation is an affront to the divine. In many theologies, creation is meant to be sustained, a delicate balance that mirrors the harmony of the divine order. Fiat systems—by continuously printing money and driving inflation—treat nature and humanity as expendable resources to be exploited for short-term gains, leading to environmental degradation and societal collapse. The creation narrative, in which humans are called to be stewards, is inverted. The fiat system, through its unholy alliance with unrestrained growth and unsustainable debt, is destroying the very creation it should protect.
Furthermore, the fiat system drives idolatry of power and wealth. The central banks and corporations that control the money supply have become modern-day gods, their decrees shaping the lives of billions, while the masses are enslaved by debt and inflation. This form of worship isn't overt, but it is profound. It leads to a world where people place their faith not in God or their families, but in the abstract promises of institutions that serve their own interests.
Physics and the Infinite Growth Paradox
Physics teaches us that the universe is finite—resources, energy, and space are all limited. Yet, the fiat system operates under the delusion of infinite growth. Central banks print money without concern for natural limits, encouraging an economy that assumes unending expansion. This is not only an economic fallacy; it is a physical impossibility.
In thermodynamics, the Second Law states that entropy (disorder) increases over time in any closed system. The fiat system operates as if the Earth were an infinite resource pool, perpetually able to expand without consequence. The real world, however, does not bend to these abstract concepts of infinite growth. Resources are finite, ecosystems are fragile, and human capacity is limited. Fiat currency, by promoting unsustainable consumption and growth, accelerates the depletion of resources and the degradation of natural systems that support life itself.
Even the financial “growth” driven by fiat policies leads to unsustainable bubbles—inflated stock markets, real estate, and speculative assets that burst and leave ruin in their wake. These crashes aren’t just economic—they have profound biological consequences. The cycles of boom and bust undermine communities, erode social stability, and increase anxiety and depression, all of which affect human health at a biological level.
Biology: The Fiat System and the Destruction of Human Health
Biologically, the fiat system is a cancerous growth on human society. The constant chase for growth and the devaluation of work leads to chronic stress, which is one of the leading causes of disease in modern society. The strain of living in a system that values speculation over well-being results in a biological feedback loop: rising anxiety, poor mental health, physical diseases like cardiovascular disorders, and a shortening of lifespans.
Moreover, the focus on profit and short-term returns creates a biological disconnect between humans and the planet. The fiat system fuels industries that destroy ecosystems, increase pollution, and deplete resources at unsustainable rates. These actions are not just environmentally harmful; they directly harm human biology. The degradation of the environment—whether through toxic chemicals, pollution, or resource extraction—has profound biological effects on human health, causing respiratory diseases, cancers, and neurological disorders.
The biological cost of the fiat system is not a distant theory; it is being paid every day by millions in the form of increased health risks, diseases linked to stress, and the growing burden of mental health disorders. The constant uncertainty of an inflation-driven economy exacerbates these conditions, creating a society of individuals whose bodies and minds are under constant strain. We are witnessing a systemic biological unraveling, one in which the very act of living is increasingly fraught with pain, instability, and the looming threat of collapse.
Finance as the Final Illusion
At the core of the fiat system is a fundamental illusion—that financial growth can occur without any real connection to tangible value. The abstraction of currency, the manipulation of interest rates, and the constant creation of new money hide the underlying truth: the system is built on nothing but faith. When that faith falters, the entire system collapses.
This illusion has become so deeply embedded that it now defines the human experience. Work no longer connects to production or creation—it is reduced to a transaction on a spreadsheet, a means to acquire more fiat currency in a world where value is ephemeral and increasingly disconnected from human reality.
As we pursue ever-expanding wealth, the fundamental truths of biology—interdependence, sustainability, and balance—are ignored. The fiat system’s abstract financial models serve to disconnect us from the basic realities of life: that we are part of an interconnected world where every action has a reaction, where resources are finite, and where human health, both mental and physical, depends on the stability of our environment and our social systems.
The Ultimate Extermination
In the end, the fiat system is not just an economic issue; it is a biological, philosophical, theological, and existential threat to the very survival of humanity. It is a force that devalues human effort, encourages environmental destruction, fosters inequality, and creates pain at the core of the human biological condition. It is an economic framework that leads not to prosperity, but to extermination—not just of species, but of the very essence of human well-being.
To continue on this path is to accept the slow death of our species, one based not on natural forces, but on our own choice to worship the abstract over the real, the speculative over the tangible. The fiat system isn't just a threat; it is the ultimate self-inflicted wound, a cultural and financial cancer that, if left unchecked, will destroy humanity’s chance for survival and peace.
-
 @ 491afeba:8b64834e
2025-05-27 23:57:01
@ 491afeba:8b64834e
2025-05-27 23:57:01Quando adolescente eu acreditava na coerência da teoria de "amor líquido" do polonês, sociólogo, Zygmunt Bauman, apresentada no livro "Amor Líquido: Sobre a Fragilidade dos Laços Humanos", qual no meu amadurecimento em estudos, sejam eles no meio acadêmico ou fora, percebo como uma das formas mais rasas de explicar as mudanças e transformações dos padrões de relações sócio-afetivas dos humanos. A seguir colocar-me-ei na minha juventude não tanto recente, direi então que nós, se adolescentes e conservadores, ou mesmo jovens adultos mais conservadores, costumamos levar como dogma uma óptica decadentista generalizada de todos os avanços de eras dos homens, universalizamos por nos ser comum a indistinção entre humanidade e humanidades, ou mesmo "humanity" e "humankind" ("humanidade" como espécime e "humanidade" como um universal), compreendemos toda "essas" como "essa" e indistinguimos as sociedades para com os homens, ou seja, a incapacidade de definir os seres dentro de suas respectivas singularidades e especificidades nos leva ao decadentismo generalista (a crença de que de forma geral, e universal, a "civilização universal" decai moralmente, éticamente, materialmente e espiritualmente), que aparente à nós determinadas mudanças nas relações humanas quanto ao caráter sócio-afetivo, por falta de profundidade e critérios ainda sobre questões alinhadas aos métodos e coerências, ou incoerências, lógicas, nós se jovens e conservadores somos levados ao engodo de concordar com a teoria do amor líquido de Bauman, que devo cá explicar de antemão: trata ela, a teoria, o padrão de "amor" dos tempos presentes como frágil, de prazo (curto e médio) e diferente em grau comparativamente ao amor comum das eras passadas.
Aos jovens mais progressistas opera uma compreensão dialética sobre as eras dos homens nos seu tempo presente, na qual ao tempo que o ser progride ele também regride simultaneamente, ou seja, a medida que aparecem contradições advindas de transformações materiais da realidade humana o ser supera essas contradições e progride em meio as transformações, ainda fazendo parte da lógica dessa indissociavelmente, assim constantemente progredindo e regredindo, havendo para esses dois vetores de distinção: o primeiro é o que releva questões espirituais como ao caráter do pensamento "new age", o segundo ignora essas questões por negar a existência da alma, seguem ao materialismo. Cedem em crer na teoria baumaninana como dogma, pois não encontram outros meios para explicar as transformações da sociedade na esfera sócio-afetiva sem que haja confrontamento direto com determinadas premissas assim pertinemente presentes, ou por não conciliarem com análises relativamente superiores, como a de Anthony Giddens sobre a "relação pura" em "A Transformação da Intimidade" e de François de Singly apresentada em "Sociologie du Couple".
https://i.pinimg.com/736x/6f/b4/9e/6fb49eda2c8cf6dc837a0abfc7e108e6.jpg
Há um problema quando uma teoria deixa de assim ser para vir a tornar-se mais um elemento desconexo da ciência, agora dentro da cultura pop, se assim podemos dizer, ou da cultura de massa, ou se preferirem mesmo "anticultura", esse problema é a sua deformização teórica, tornando-se essa rasa para sua palatabilidade massiva, somada a incapacidade de partes da sociedade civil em compreender as falhas daquilo que já foi massificado. Tive surpresa ao entender que muitos outros compartilham da mesma opinião, a exemplo, possuo um amigo na faculdade, marxista, que ao falarmos sobre nossos projetos de pesquisa, citou ele o projeto de um de nossos colegas, no qual esse referido um de nossos colegas faria seu projeto com base na teoria do amor líquido de Bauman, então alí demos risada disso, ora, para nós a teoria baumaniana é furada, passamos a falar sobre Bauman e o motivo pelo qual não gostávamos, lá fiquei até surpreso em saber que mais gente além de mim não gostava da teoria de Bauman, pois ao que eu via na internet era rede de enaltecimentos à figura e à sua teoria, tal como fosse uma revelação partindo de alguma divindade da Idade do Bronze. Pouco tempo depois tive em aula de teoria política uma citação de Bauman partindo do professor que ministrava a disciplina, no entanto, ao citar o nome de Bauman o mesmo fez uma feição na qual aparentava segurar risada, provavelmente ele também não levava Bauman à sério. Não devo negar que todas as vezes que vejo o sociólogo sendo citado em alguma nota no X, no Instagram ou qualquer outra rede social, tal como fosse um referencial teórico bom, sinto uma vergonha alheia pois alí tenho uma impressão de que a pessoa não leu Bauman e usa o referencial teórico como um fato já assim provado e comprovado.
Há pontos positivos na teoria baumaniana, como a capacidade de perceber o problema e correlacioná-lo à modernidade, assim como sucitar a influência do que há de material no fenômeno, porém os erros são pertinentes: o primeiro problema é de categoria. Não há, por parte de Bauman noção alguma entre as dissociações dos amores, não há atenção sobre o amor como estrutura ou ele como um sentimento, todo ele é compreendido uniformemente como "amor", partindo do pressuposto que todas as relações, todas elas, são firmadas com base no amor. Essa crença tem uma origem: Hegel. Nos Escritos Teológicos Hegel partia da crença que o amor ligava os seres relacionalmente como uma força de superação e alienação, mas há de compreendermos que esse Friedrich Hegel é o jovem ainda pouco maduro em suas ideias e seu sistema de pensamento, mais a frente, em "Fenomenologia do Espírito e na Filosofia do Direito", Hegel compreende a institucionalidade do direito no amor e a institucionalização dessa força, assim aproxima-se da realidade a respeito da inserção do amor nas esferas práticas do humano, porém essa ideia, apesar de imperfeita, pois ao que sabemos não é o amor que consolida a relação, mas sim a Verdade (Alétheia), conforme apontado por Heidegger em "Ser e Tempo", essa ideia do amor como a fundamento das relações humanas influenciou, e até hoje influencia, qualquer análise sobre as relações humanas fora da esfera materialista, fora dessa pois, melhormente explicado em exemplo, os marxistas (em exemplo), assim como Marx, consideram como base primordial das relações as condições materiais.
Por certo, não é de todo amor a base para a solidificação, ora, erram aqueles que creem que somente essa força, assim apontada por Hegel, constituiam todos os relacionamentos formais como pilares fundamentais, pois em prática as famílias eram até a fiduciarização dessas, por mais paradoxal que seja, compreendidas melhor como instituições orgânicas de caráter legal do que conluios de afetividades. A família outrora tinha consigo aparelhos de hierarquia bem estabelicidos, quais prezavam pela ordem interna e externa, que acima dessa instituição estava somente a Igreja (outra instituição), com sua fiduciarização [da família] após o movimento tomado pelos Estados nacionais em aplicação do casamento civil mudou-se a lógica das partes que a compõe, findou-se o princípio da subsidiariedade (não intervenção de determinadas instituições nas decisões quais podem ser exercidas em resuluções de problemas nas competências de quaisquer instituições), foi-se então, contudo, também a autoridade, e nisso revela-se um outro problema não apontado na teoria de Bauman: qual o padrão do amor "sólido"? Pois, ora, sociedades tradicionais não abdicavam do relevar dos amores para tornar seus filhos em ativos nas práticas de trocas (dádivas)? É notório que esse padrão se dissocia do padrão de sentimento apontado por Bauman, encontramos esse fato em estudo nos trabalhos "Ensaio Sobre a Dádiva", do Marcel Mauss, e "As Estruturas Elementares do Parentesco", do Claude Levi-Strauss, quais expõem que nas sociedades "sólidas", tradicionais, relevava-se mais questões institucionais que as sentimentais para a formação de laços (teoria da aliança). Muitas das relações passadas não eram baseadas no amor, não significando assim que as de hoje, em oposição, sejam, mas que permanecem-se semelhantes em base, diferentemente em grau e forma.
https://substackcdn.com/image/fetch/f_auto,q_auto:good,fl_progressive:steep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2F748b94c3-f882-45db-8333-09260ef15cfe_615x413.jpeg
Ora, ainda existem casamentos motivados pela política, pelo status, pelo prestígio, pelos bens, pelo poder, pela influência familiar e assim sucetivamente, tal como no passado, ocorre que essa prática tornou-se oculta, não mais explícita e aparente, devo dizer ainda que em partes, pois prepondera em nosso tempo uma epidemia de adultérios, fornicações, práticas lascivas e demais práticas libertinosas explicitamente, em contraposição às práticas ocultas em vergonhas de sociedades sem declínio moral e espiritual, o que nos leva a questionar o método comparativo em dicotomia temporal "presente x passado" aplicado por Bauman, no qual segue-se da seguinte forma:
Transformação Passado = *sólido* | Presente = *líquido* Categorias Padrão de amor: tradicional (*sólido*) moderno (*líquido*) *Sólido* = estável, prazo (médio-grande), profundo, determinado. *Líquido* = instável, prazo (curto-médio), raso, indeterminado.O que penso é: Zygmunt Bauman buscou uma explicação material e laical para desviar ao fato de que há uma notória correlação entre espiritualização da sociedade, se voltada à Verdade, com a estabilidade das instituições, o que é já reduzido à moral religiosa, somente, não à mística, como por pensadores da linha de Tocqueville, ou em abordagens também mais laical (positivista) porém ainda relevantes, como Émile Durkheim em "As Formas Elementares da Vida Religiosa" e Max Weber em "A Ética Protestante e o Espírito do Capitalismo", contrapondo uma abordage mais voltada, de fato, a espiritualidade, como Christopher Dawnson, que defende essa teoria em "Religião e o Surgimento da Cultura Ocidental", e Eric Voegelin, principalmente nas obras "A Nova Ciência da Política" e "Ordem e História".
Encerrando, minha cosmovisão é a católica, o sistema de crença e religião qual sigo é do Deus que se fez homem por amor aos seus filhos, não posso negar ou mesmo omitir o fato de que, por trás de toda a minha crítica estão meus pensamentos e minhas convicções alinhadas àquilo que mais tenho amor em toda minha vida: a Verdade, e a Verdade é Deus, pois Cristo é a Verdade, o Caminho e a Vida, ninguém vai ao Pai se não por Ele, e pois bem, seria incoerência de minha parte não relevar o fato de crença como um dos motivos pelos quais eu rejeito a teoria do amor líquido de Zygmunt Bauman, pois os amores são todos eles praticados por formas, existem por diferentes formas e assim são desde sua tradicionalidade até o predomínio das distorções de declínio espiritual das eras presentes (e também antigas pré-Era Axial), estão esses preservados pelo alinhamento à verdade, assim são indistorcíveis, imutáveis, ou seja, amor é amor, não releva-se o falso amor como um, simplesmente não o é, assim o interesse, a sanha por bens, o egoísmo e a egolatria ("cupiditas", para Santo Agostinho de Hipona, em oposição ao que o santo e filósofo trata por "caritas") não são formas do amor, são autoenganos, não bons, se não são bons logo não são de Deus, ora, se Deus é amor, se ele nos ama, determino como amor (e suas formas) o que está de acordo com a Verdade. Aprofundando, a Teologia do Corpo, do Papa São João Paulo II, rejeita a "liquidez" apresentada por Bauman, pois o amor é, em suma, sacríficio, parte da entrega total de si ao próximo, e se não há logo não é amor. A Teologia do Corpo rejeita não os fundamentos de mentira no "líquido", mas também no "sólido", pois a tradicionalidade não é sinônimo de bom e pleno acordo com o amor que Deus pede de nós, não são as coerções, as violências, as imposições e demais vontades em oposição às de Deus que determinam os amores -- fatos em oposição ao ideário romanticizado. Claro, nem todas as coerções são por si inválidas do amor, ou mesmo as escolhas em trocas racionalizadas, a exemplo do autruísmo em vista da chance da família ter êxito e sucesso, ou seja, pelo bem dos próximos haver a necessidade de submissão a, em exemplo, um casamento forjado, ou algo do gênero, reconhece-se o amor no ato se feito por bem da família, porém o amor incutido, nesse caso, explicita o caráter sacrificial, no qual uma vontade e um amor genuinamente potencial em prazeres e alegrias são anulados, ou seja, mesmo nesse modelo tradicional na "solidez" há possibilidade do amor, não nas formas romanticizadas em critérios, como "estabilidade" e "durabilidade", mas no caráter do sacríficio exercido. Conforme nos ensina São Tomás de Aquino, o amor não é uma "força", tal como ensina Hegel, mas sim uma virtude teologal conforme na "Suma Teológica" (II-II Q. 26-28), não devemos reduzir o amor e os amores em análises simplórias (não simples) de falsa complexidade extraídas em métodos questionáveis e pouco competentes à real diensão de crise espiritual das eras, por esse motivo não concordo com a teoria do amor líquido de Zygmunt Bauman.
-
 @ a367f9eb:0633efea
2024-12-22 21:35:22
@ a367f9eb:0633efea
2024-12-22 21:35:22I’ll admit that I was wrong about Bitcoin. Perhaps in 2013. Definitely 2017. Probably in 2018-2019. And maybe even today.
Being wrong about Bitcoin is part of finally understanding it. It will test you, make you question everything, and in the words of BTC educator and privacy advocate Matt Odell, “Bitcoin will humble you”.
I’ve had my own stumbles on the way.
In a very public fashion in 2017, after years of using Bitcoin, trying to start a company with it, using it as my primary exchange vehicle between currencies, and generally being annoying about it at parties, I let out the bear.
In an article published in my own literary magazine Devolution Review in September 2017, I had a breaking point. The article was titled “Going Bearish on Bitcoin: Cryptocurrencies are the tulip mania of the 21st century”.
It was later republished in Huffington Post and across dozens of financial and crypto blogs at the time with another, more appropriate title: “Bitcoin Has Become About The Payday, Not Its Potential”.
As I laid out, my newfound bearishness had little to do with the technology itself or the promise of Bitcoin, and more to do with the cynical industry forming around it:
In the beginning, Bitcoin was something of a revolution to me. The digital currency represented everything from my rebellious youth.
It was a decentralized, denationalized, and digital currency operating outside the traditional banking and governmental system. It used tools of cryptography and connected buyers and sellers across national borders at minimal transaction costs.
…
The 21st-century version (of Tulip mania) has welcomed a plethora of slick consultants, hazy schemes dressed up as investor possibilities, and too much wishy-washy language for anything to really make sense to anyone who wants to use a digital currency to make purchases.
While I called out Bitcoin by name at the time, on reflection, I was really talking about the ICO craze, the wishy-washy consultants, and the altcoin ponzis.
What I was articulating — without knowing it — was the frame of NgU, or “numbers go up”. Rather than advocating for Bitcoin because of its uncensorability, proof-of-work, or immutability, the common mentality among newbies and the dollar-obsessed was that Bitcoin mattered because its price was a rocket ship.
And because Bitcoin was gaining in price, affinity tokens and projects that were imperfect forks of Bitcoin took off as well.
The price alone — rather than its qualities — were the reasons why you’d hear Uber drivers, finance bros, or your gym buddy mention Bitcoin. As someone who came to Bitcoin for philosophical reasons, that just sat wrong with me.
Maybe I had too many projects thrown in my face, or maybe I was too frustrated with the UX of Bitcoin apps and sites at the time. No matter what, I’ve since learned something.
I was at least somewhat wrong.
My own journey began in early 2011. One of my favorite radio programs, Free Talk Live, began interviewing guests and having discussions on the potential of Bitcoin. They tied it directly to a libertarian vision of the world: free markets, free people, and free banking. That was me, and I was in. Bitcoin was at about $5 back then (NgU).
I followed every article I could, talked about it with guests on my college radio show, and became a devoted redditor on r/Bitcoin. At that time, at least to my knowledge, there was no possible way to buy Bitcoin where I was living. Very weak.
I was probably wrong. And very wrong for not trying to acquire by mining or otherwise.
The next year, after moving to Florida, Bitcoin was a heavy topic with a friend of mine who shared the same vision (and still does, according to the Celsius bankruptcy documents). We talked about it with passionate leftists at Occupy Tampa in 2012, all the while trying to explain the ills of Keynesian central banking, and figuring out how to use Coinbase.
I began writing more about Bitcoin in 2013, writing a guide on “How to Avoid Bank Fees Using Bitcoin,” discussing its potential legalization in Germany, and interviewing Jeremy Hansen, one of the first political candidates in the U.S. to accept Bitcoin donations.
Even up until that point, I thought Bitcoin was an interesting protocol for sending and receiving money quickly, and converting it into fiat. The global connectedness of it, plus this cypherpunk mentality divorced from government control was both useful and attractive. I thought it was the perfect go-between.
But I was wrong.
When I gave my first public speech on Bitcoin in Vienna, Austria in December 2013, I had grown obsessed with Bitcoin’s adoption on dark net markets like Silk Road.
My theory, at the time, was the number and price were irrelevant. The tech was interesting, and a novel attempt. It was unlike anything before. But what was happening on the dark net markets, which I viewed as the true free market powered by Bitcoin, was even more interesting. I thought these markets would grow exponentially and anonymous commerce via BTC would become the norm.
While the price was irrelevant, it was all about buying and selling goods without permission or license.
Now I understand I was wrong.
Just because Bitcoin was this revolutionary technology that embraced pseudonymity did not mean that all commerce would decentralize as well. It did not mean that anonymous markets were intended to be the most powerful layer in the Bitcoin stack.
What I did not even anticipate is something articulated very well by noted Bitcoin OG Pierre Rochard: Bitcoin as a savings technology.
The ability to maintain long-term savings, practice self-discipline while stacking stats, and embrace a low-time preference was just not something on the mind of the Bitcoiners I knew at the time.
Perhaps I was reading into the hype while outwardly opposing it. Or perhaps I wasn’t humble enough to understand the true value proposition that many of us have learned years later.
In the years that followed, I bought and sold more times than I can count, and I did everything to integrate it into passion projects. I tried to set up a company using Bitcoin while at my university in Prague.
My business model depended on university students being technologically advanced enough to have a mobile wallet, own their keys, and be able to make transactions on a consistent basis. Even though I was surrounded by philosophically aligned people, those who would advance that to actually put Bitcoin into practice were sparse.
This is what led me to proclaim that “Technological Literacy is Doomed” in 2016.
And I was wrong again.
Indeed, since that time, the UX of Bitcoin-only applications, wallets, and supporting tech has vastly improved and onboarded millions more people than anyone thought possible. The entrepreneurship, coding excellence, and vision offered by Bitcoiners of all stripes have renewed a sense in me that this project is something built for us all — friends and enemies alike.
While many of us were likely distracted by flashy and pumpy altcoins over the years (me too, champs), most of us have returned to the Bitcoin stable.
Fast forward to today, there are entire ecosystems of creators, activists, and developers who are wholly reliant on the magic of Bitcoin’s protocol for their life and livelihood. The options are endless. The FUD is still present, but real proof of work stands powerfully against those forces.
In addition, there are now dozens of ways to use Bitcoin privately — still without custodians or intermediaries — that make it one of the most important assets for global humanity, especially in dictatorships.
This is all toward a positive arc of innovation, freedom, and pure independence. Did I see that coming? Absolutely not.
Of course, there are probably other shots you’ve missed on Bitcoin. Price predictions (ouch), the short-term inflation hedge, or the amount of institutional investment. While all of these may be erroneous predictions in the short term, we have to realize that Bitcoin is a long arc. It will outlive all of us on the planet, and it will continue in its present form for the next generation.
Being wrong about the evolution of Bitcoin is no fault, and is indeed part of the learning curve to finally understanding it all.
When your family or friends ask you about Bitcoin after your endless sessions explaining market dynamics, nodes, how mining works, and the genius of cryptographic signatures, try to accept that there is still so much we have to learn about this decentralized digital cash.
There are still some things you’ve gotten wrong about Bitcoin, and plenty more you’ll underestimate or get wrong in the future. That’s what makes it a beautiful journey. It’s a long road, but one that remains worth it.
-
 @ 6389be64:ef439d32
2024-12-09 23:50:41
@ 6389be64:ef439d32
2024-12-09 23:50:41Resilience is the ability to withstand shocks, adapt, and bounce back. It’s an essential quality in nature and in life. But what if we could take resilience a step further? What if, instead of merely surviving, a system could improve when faced with stress? This concept, known as anti-fragility, is not just theoretical—it’s practical. Combining two highly resilient natural tools, comfrey and biochar, reveals how we can create systems that thrive under pressure and grow stronger with each challenge.
Comfrey: Nature’s Champion of Resilience
Comfrey is a plant that refuses to fail. Once its deep roots take hold, it thrives in poor soils, withstands drought, and regenerates even after being cut down repeatedly. It’s a hardy survivor, but comfrey doesn’t just endure—it contributes. Known as a dynamic accumulator, it mines nutrients from deep within the earth and brings them to the surface, making them available for other plants.
Beyond its ecological role, comfrey has centuries of medicinal use, earning the nickname "knitbone." Its leaves can heal wounds and restore health, a perfect metaphor for resilience. But as impressive as comfrey is, its true potential is unlocked when paired with another resilient force: biochar.
Biochar: The Silent Powerhouse of Soil Regeneration
Biochar, a carbon-rich material made by burning organic matter in low-oxygen conditions, is a game-changer for soil health. Its unique porous structure retains water, holds nutrients, and provides a haven for beneficial microbes. Soil enriched with biochar becomes drought-resistant, nutrient-rich, and biologically active—qualities that scream resilience.
Historically, ancient civilizations in the Amazon used biochar to transform barren soils into fertile agricultural hubs. Known as terra preta, these soils remain productive centuries later, highlighting biochar’s remarkable staying power.
Yet, like comfrey, biochar’s potential is magnified when it’s part of a larger system.
The Synergy: Comfrey and Biochar Together
Resilience turns into anti-fragility when systems go beyond mere survival and start improving under stress. Combining comfrey and biochar achieves exactly that.
-
Nutrient Cycling and Retention\ Comfrey’s leaves, rich in nitrogen, potassium, and phosphorus, make an excellent mulch when cut and dropped onto the soil. However, these nutrients can wash away in heavy rains. Enter biochar. Its porous structure locks in the nutrients from comfrey, preventing runoff and keeping them available for plants. Together, they create a system that not only recycles nutrients but amplifies their effectiveness.
-
Water Management\ Biochar holds onto water making soil not just drought-resistant but actively water-efficient, improving over time with each rain and dry spell.
-
Microbial Ecosystems\ Comfrey enriches soil with organic matter, feeding microbial life. Biochar provides a home for these microbes, protecting them and creating a stable environment for them to multiply. Together, they build a thriving soil ecosystem that becomes more fertile and resilient with each passing season.
Resilient systems can withstand shocks, but anti-fragile systems actively use those shocks to grow stronger. Comfrey and biochar together form an anti-fragile system. Each addition of biochar enhances water and nutrient retention, while comfrey regenerates biomass and enriches the soil. Over time, the system becomes more productive, less dependent on external inputs, and better equipped to handle challenges.
This synergy demonstrates the power of designing systems that don’t just survive—they thrive.
Lessons Beyond the Soil
The partnership of comfrey and biochar offers a valuable lesson for our own lives. Resilience is an admirable trait, but anti-fragility takes us further. By combining complementary strengths and leveraging stress as an opportunity, we can create systems—whether in soil, business, or society—that improve under pressure.
Nature shows us that resilience isn’t the end goal. When we pair resilient tools like comfrey and biochar, we unlock a system that evolves, regenerates, and becomes anti-fragile. By designing with anti-fragility in mind, we don’t just bounce back, we bounce forward.
By designing with anti-fragility in mind, we don’t just bounce back, we bounce forward.
-
-
 @ e31e84c4:77bbabc0
2024-12-02 10:44:07
@ e31e84c4:77bbabc0
2024-12-02 10:44:07Bitcoin and Fixed Income was Written By Wyatt O’Rourke. If you enjoyed this article then support his writing, directly, by donating to his lightning wallet: ultrahusky3@primal.net
Fiduciary duty is the obligation to act in the client’s best interests at all times, prioritizing their needs above the advisor’s own, ensuring honesty, transparency, and avoiding conflicts of interest in all recommendations and actions.
This is something all advisors in the BFAN take very seriously; after all, we are legally required to do so. For the average advisor this is a fairly easy box to check. All you essentially have to do is have someone take a 5-minute risk assessment, fill out an investment policy statement, and then throw them in the proverbial 60/40 portfolio. You have thousands of investment options to choose from and you can reasonably explain how your client is theoretically insulated from any move in the \~markets\~. From the traditional financial advisor perspective, you could justify nearly anything by putting a client into this type of portfolio. All your bases were pretty much covered from return profile, regulatory, compliance, investment options, etc. It was just too easy. It became the household standard and now a meme.
As almost every real bitcoiner knows, the 60/40 portfolio is moving into psyop territory, and many financial advisors get clowned on for defending this relic on bitcoin twitter. I’m going to specifically poke fun at the ‘40’ part of this portfolio.
The ‘40’ represents fixed income, defined as…
An investment type that provides regular, set interest payments, such as bonds or treasury securities, and returns the principal at maturity. It’s generally considered a lower-risk asset class, used to generate stable income and preserve capital.
Historically, this part of the portfolio was meant to weather the volatility in the equity markets and represent the “safe” investments. Typically, some sort of bond.
First and foremost, the fixed income section is most commonly constructed with U.S. Debt. There are a couple main reasons for this. Most financial professionals believe the same fairy tale that U.S. Debt is “risk free” (lol). U.S. debt is also one of the largest and most liquid assets in the market which comes with a lot of benefits.
There are many brilliant bitcoiners in finance and economics that have sounded the alarm on the U.S. debt ticking time bomb. I highly recommend readers explore the work of Greg Foss, Lawrence Lepard, Lyn Alden, and Saifedean Ammous. My very high-level recap of their analysis:
-
A bond is a contract in which Party A (the borrower) agrees to repay Party B (the lender) their principal plus interest over time.
-
The U.S. government issues bonds (Treasury securities) to finance its operations after tax revenues have been exhausted.
-
These are traditionally viewed as “risk-free” due to the government’s historical reliability in repaying its debts and the strength of the U.S. economy
-
U.S. bonds are seen as safe because the government has control over the dollar (world reserve asset) and, until recently (20 some odd years), enjoyed broad confidence that it would always honor its debts.
-
This perception has contributed to high global demand for U.S. debt but, that is quickly deteriorating.
-
The current debt situation raises concerns about sustainability.
-
The U.S. has substantial obligations, and without sufficient productivity growth, increasing debt may lead to a cycle where borrowing to cover interest leads to more debt.
-
This could result in more reliance on money creation (printing), which can drive inflation and further debt burdens.
In the words of Lyn Alden “Nothing stops this train”
Those obligations are what makes up the 40% of most the fixed income in your portfolio. So essentially you are giving money to one of the worst capital allocators in the world (U.S. Gov’t) and getting paid back with printed money.
As someone who takes their fiduciary responsibility seriously and understands the debt situation we just reviewed, I think it’s borderline negligent to put someone into a classic 60% (equities) / 40% (fixed income) portfolio without serious scrutiny of the client’s financial situation and options available to them. I certainly have my qualms with equities at times, but overall, they are more palatable than the fixed income portion of the portfolio. I don’t like it either, but the money is broken and the unit of account for nearly every equity or fixed income instrument (USD) is fraudulent. It’s a paper mache fade that is quite literally propped up by the money printer.
To briefly be as most charitable as I can – It wasn’t always this way. The U.S. Dollar used to be sound money, we used to have government surplus instead of mathematically certain deficits, The U.S. Federal Government didn’t used to have a money printing addiction, and pre-bitcoin the 60/40 portfolio used to be a quality portfolio management strategy. Those times are gone.
Now the fun part. How does bitcoin fix this?
Bitcoin fixes this indirectly. Understanding investment criteria changes via risk tolerance, age, goals, etc. A client may still have a need for “fixed income” in the most literal definition – Low risk yield. Now you may be thinking that yield is a bad word in bitcoin land, you’re not wrong, so stay with me. Perpetual motion machine crypto yield is fake and largely where many crypto scams originate. However, that doesn’t mean yield in the classic finance sense does not exist in bitcoin, it very literally does. Fortunately for us bitcoiners there are many other smart, driven, and enterprising bitcoiners that understand this problem and are doing something to address it. These individuals are pioneering new possibilities in bitcoin and finance, specifically when it comes to fixed income.
Here are some new developments –
Private Credit Funds – The Build Asset Management Secured Income Fund I is a private credit fund created by Build Asset Management. This fund primarily invests in bitcoin-backed, collateralized business loans originated by Unchained, with a secured structure involving a multi-signature, over-collateralized setup for risk management. Unchained originates loans and sells them to Build, which pools them into the fund, enabling investors to share in the interest income.
Dynamics
- Loan Terms: Unchained issues loans at interest rates around 14%, secured with a 2/3 multi-signature vault backed by a 40% loan-to-value (LTV) ratio.
- Fund Mechanics: Build buys these loans from Unchained, thus providing liquidity to Unchained for further loan originations, while Build manages interest payments to investors in the fund.
Pros
- The fund offers a unique way to earn income via bitcoin-collateralized debt, with protection against rehypothecation and strong security measures, making it attractive for investors seeking exposure to fixed income with bitcoin.
Cons
- The fund is only available to accredited investors, which is a regulatory standard for private credit funds like this.
Corporate Bonds – MicroStrategy Inc. (MSTR), a business intelligence company, has leveraged its corporate structure to issue bonds specifically to acquire bitcoin as a reserve asset. This approach allows investors to indirectly gain exposure to bitcoin’s potential upside while receiving interest payments on their bond investments. Some other publicly traded companies have also adopted this strategy, but for the sake of this article we will focus on MSTR as they are the biggest and most vocal issuer.
Dynamics
-
Issuance: MicroStrategy has issued senior secured notes in multiple offerings, with terms allowing the company to use the proceeds to purchase bitcoin.
-
Interest Rates: The bonds typically carry high-yield interest rates, averaging around 6-8% APR, depending on the specific issuance and market conditions at the time of issuance.
-
Maturity: The bonds have varying maturities, with most structured for multi-year terms, offering investors medium-term exposure to bitcoin’s value trajectory through MicroStrategy’s holdings.
Pros
-
Indirect Bitcoin exposure with income provides a unique opportunity for investors seeking income from bitcoin-backed debt.
-
Bonds issued by MicroStrategy offer relatively high interest rates, appealing for fixed-income investors attracted to the higher risk/reward scenarios.
Cons
-
There are credit risks tied to MicroStrategy’s financial health and bitcoin’s performance. A significant drop in bitcoin prices could strain the company’s ability to service debt, increasing credit risk.
-
Availability: These bonds are primarily accessible to institutional investors and accredited investors, limiting availability for retail investors.
Interest Payable in Bitcoin – River has introduced an innovative product, bitcoin Interest on Cash, allowing clients to earn interest on their U.S. dollar deposits, with the interest paid in bitcoin.
Dynamics
-
Interest Payment: Clients earn an annual interest rate of 3.8% on their cash deposits. The accrued interest is converted to Bitcoin daily and paid out monthly, enabling clients to accumulate Bitcoin over time.
-
Security and Accessibility: Cash deposits are insured up to $250,000 through River’s banking partner, Lead Bank, a member of the FDIC. All Bitcoin holdings are maintained in full reserve custody, ensuring that client assets are not lent or leveraged.
Pros
-
There are no hidden fees or minimum balance requirements, and clients can withdraw their cash at any time.
-
The 3.8% interest rate provides a predictable income stream, akin to traditional fixed-income investments.
Cons
-
While the interest rate is fixed, the value of the Bitcoin received as interest can fluctuate, introducing potential variability in the investment’s overall return.
-
Interest rate payments are on the lower side
Admittedly, this is a very small list, however, these types of investments are growing more numerous and meaningful. The reality is the existing options aren’t numerous enough to service every client that has a need for fixed income exposure. I challenge advisors to explore innovative options for fixed income exposure outside of sovereign debt, as that is most certainly a road to nowhere. It is my wholehearted belief and call to action that we need more options to help clients across the risk and capital allocation spectrum access a sound money standard.
Additional Resources
-
River: The future of saving is here: Earn 3.8% on cash. Paid in Bitcoin.
-
MicroStrategy: MicroStrategy Announces Pricing of Offering of Convertible Senior Notes
Bitcoin and Fixed Income was Written By Wyatt O’Rourke. If you enjoyed this article then support his writing, directly, by donating to his lightning wallet: ultrahusky3@primal.net
-
-
 @ 87730827:746b7d35
2024-11-20 09:27:53
@ 87730827:746b7d35
2024-11-20 09:27:53Original: https://techreport.com/crypto-news/brazil-central-bank-ban-monero-stablecoins/
Brazilian’s Central Bank Will Ban Monero and Algorithmic Stablecoins in the Country
Brazil proposes crypto regulations banning Monero and algorithmic stablecoins and enforcing strict compliance for exchanges.
KEY TAKEAWAYS
- The Central Bank of Brazil has proposed regulations prohibiting privacy-centric cryptocurrencies like Monero.
- The regulations categorize exchanges into intermediaries, custodians, and brokers, each with specific capital requirements and compliance standards.
- While the proposed rules apply to cryptocurrencies, certain digital assets like non-fungible tokens (NFTs) are still ‘deregulated’ in Brazil.

In a Notice of Participation announcement, the Brazilian Central Bank (BCB) outlines regulations for virtual asset service providers (VASPs) operating in the country.
In the document, the Brazilian regulator specifies that privacy-focused coins, such as Monero, must be excluded from all digital asset companies that intend to operate in Brazil.
Let’s unpack what effect these regulations will have.
Brazil’s Crackdown on Crypto Fraud
If the BCB’s current rule is approved, exchanges dealing with coins that provide anonymity must delist these currencies or prevent Brazilians from accessing and operating these assets.
The Central Bank argues that currencies like Monero make it difficult and even prevent the identification of users, thus creating problems in complying with international AML obligations and policies to prevent the financing of terrorism.
According to the Central Bank of Brazil, the bans aim to prevent criminals from using digital assets to launder money. In Brazil, organized criminal syndicates such as the Primeiro Comando da Capital (PCC) and Comando Vermelho have been increasingly using digital assets for money laundering and foreign remittances.
… restriction on the supply of virtual assets that contain characteristics of fragility, insecurity or risks that favor fraud or crime, such as virtual assets designed to favor money laundering and terrorist financing practices by facilitating anonymity or difficulty identification of the holder.
The Central Bank has identified that removing algorithmic stablecoins is essential to guarantee the safety of users’ funds and avoid events such as when Terraform Labs’ entire ecosystem collapsed, losing billions of investors’ dollars.
The Central Bank also wants to control all digital assets traded by companies in Brazil. According to the current proposal, the national regulator will have the power to ask platforms to remove certain listed assets if it considers that they do not meet local regulations.
However, the regulations will not include NFTs, real-world asset (RWA) tokens, RWA tokens classified as securities, and tokenized movable or real estate assets. These assets are still ‘deregulated’ in Brazil.
Monero: What Is It and Why Is Brazil Banning It?
Monero ($XMR) is a cryptocurrency that uses a protocol called CryptoNote. It launched in 2013 and ‘erases’ transaction data, preventing the sender and recipient addresses from being publicly known. The Monero network is based on a proof-of-work (PoW) consensus mechanism, which incentivizes miners to add blocks to the blockchain.
Like Brazil, other nations are banning Monero in search of regulatory compliance. Recently, Dubai’s new digital asset rules prohibited the issuance of activities related to anonymity-enhancing cryptocurrencies such as $XMR.
Furthermore, exchanges such as Binance have already announced they will delist Monero on their global platforms due to its anonymity features. Kraken did the same, removing Monero for their European-based users to comply with MiCA regulations.
Data from Chainalysis shows that Brazil is the seventh-largest Bitcoin market in the world.

In Latin America, Brazil is the largest market for digital assets. Globally, it leads in the innovation of RWA tokens, with several companies already trading this type of asset.
In Closing
Following other nations, Brazil’s regulatory proposals aim to combat illicit activities such as money laundering and terrorism financing.
Will the BCB’s move safeguard people’s digital assets while also stimulating growth and innovation in the crypto ecosystem? Only time will tell.
References
Cassio Gusson is a journalist passionate about technology, cryptocurrencies, and the nuances of human nature. With a career spanning roles as Senior Crypto Journalist at CriptoFacil and Head of News at CoinTelegraph, he offers exclusive insights on South America’s crypto landscape. A graduate in Communication from Faccamp and a post-graduate in Globalization and Culture from FESPSP, Cassio explores the intersection of governance, decentralization, and the evolution of global systems.
-
 @ bf47c19e:c3d2573b
2025-05-27 21:19:32
@ bf47c19e:c3d2573b
2025-05-27 21:19:32Originalni tekst na bitcoin-balkan.com.
Pregled sadržaja
- Procena vrednosti
- Većina Bitcoin-ovih pozitivnih strana opstaje
- Broj ljudi koji su prihvatili Bitcoin
- Zaključak
Prošlo je trinaest godina od nastanka Bitcoina i lako je poverovati da je većina njegovog rasta iza njega. Deo ovoga je rezultat predrasude koju svi delimo i što nas navodi da zamislimo trenutno stanje stvari kao završni stepen njegovog razvoja. Svaki bitcoiner je nekad mislio da je prekasan sa Bitcoin-om. Međutim, kada primenjujemo kritičko razmišljanje da bismo procenili gde je Bitcoin u svojoj putanji rasta, otkrivamo da je suprotno u stvari tačno: još uvek je vrlo, vrlo rano.
Postoje dva načina da razmišljate o tome koliko je rano za Bitcoin kao zalihu vrednosti neke imovine:
-
Procena vrednosti kao procenat od njegovog punog potencijala
-
Prihvatanje kao procenat od njegovog punog potencijala (na čemu je fokus u ovom članku).
Procena vrednosti
Prvi i najčešći način da se proceni koliko je rano za Bitcoin je da se pogleda njegova ukupna vrednost (trenutno oko 900B USD) i uporedi sa njegovim punim potencijalom. Izazov sa ovim je očigledno da je puni potencijal Bitcoin-a stvar nagađanja. Oni koji duboko razumeju Bitcoin imaju tendenciju da njegov potencijal posmatraju barem kao potencijal zlata (oko 13T USD), ali teoretski više poput 200T USD (oko polovine ukupne vrednosti sveta).
Za brzi pregled ovog potencijala od 200T USD, pogledajmo ukupno raspoloživo tržište Bitcoin-a. Radi jednostavnosti, samo ćemo razmotriti njegovu ulogu zalihe vrednosti i zanemariti njegov potencijal da pojede tržišni udeo od oko 100T USD ukupne vrednosti u različitim svetskim valutama. Uzimajući u obzir različite zalihe vrednosne imovine i grubom procenom koliki bi % Bitcoin mogao da uzme od njih, dobili smo ovakav rezultat:
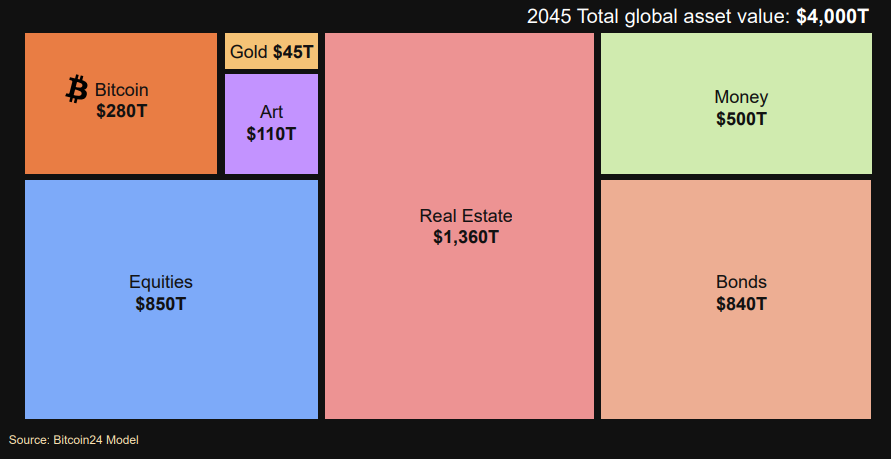
Iako put do 200T USD nije veliko rastezanje, u stvarnoj vrednosti čini se previše dobrim da bi bio istinit. Sa obzirom da je bez presedana da zaliha vrednosti neke robe postigne vrednost veću od zlata, to jednostavno predstavlja neistraženu teritoriju. Ali čak i ako se jednostavno pridržavamo targetiranja niže ciljne vrednosti zlata od 13T USD, Bitcoin još uvek tendenciju velikog porasta svoje cene u budućnosti.
Većina Bitcoin-ovih pozitivnih strana opstaje
Svako ko razmišlja da nešto svog teško zarađenog novca uskladišti u Bitcoin pita se „da li sam poranio ili zakasnio?“ Nepisano je pravilo da se svako oseća kao da je zakasnio kad stigne. Brojni su primeri ljudi koji žale kako su zakasnili 2011. ili 2013. ili 2016. godine, kada je cena Bitcoin-a bila 5, 100, odnosno 600 USD.
Kao i u bilo kojoj zajednici koja se razvija i raste i u kojoj ima manjka nekretninama, pridošlice zavide ljudima koji su već obezbedili sebi nekretninu, ne sluteći da će njima zavideti ljudi koji tek treba da dođu. Ovaj fenomen je primenjiv i na velikom broju drugih primera. Na primer, zakasneli u Kalifornijskoj zlatnoj groznici bili su razočarani kada su došli, a bogata zlatna polja su već bila iscrpljena, i umesto toga su se naseliti na nekoliko stotina hektara zemljišta, a koje sada vrede bogatstvo.
U srcu ovog osećanja je strah da više nema uspona, da više nema novca koji se može zaraditi uzimajući ono što je još uvek ostalo dostupno. Da li smo dostigli tu tačku sa Bitcoin-om?
Pa ne. Čini se da je zapravo suprotno. Na osnovu punog potencijalnog opsega procene koji smo utvrdili gore, čak i u ishodu niskog nivoa (13T USD), velika većina bogatstva koje će steći vlasnici Bitcoin-a, tek treba da se stekne (96%). Da bi parirao proceni zlata, Bitcoin i dalje mora da poraste 26 puta.
A ako se desi vrhunski ishod, punih 99,7% ukupnog stvaranja bogatstva Bitcoin-a ostaje pred nama. To bi značilo da Bitcoin još uvek treba da poraste 400 puta, zanemarujući pariranje zlatu.
Stavljanjem trenutne vrednosti Bitcoin-a u perspektivu, postaje jasno da je za Bitcoin još uvek vrlo rano.
Iako ova analiza sugeriše da za Bitcoin-u ostaje od 26x do 400x rasta, korisno je proveriti ovaj zaključak kroz drugo razumno objašnjenje, a tamo gde je poznat puni potencijal…
Broj ljudi koji su prihvatili Bitcoin
Procene broja vlasnika Bitcoin-a širom sveta se veoma razlikuju. To je dovelo do prilične količine dvosmislenosti i nesigurnosti u vezi sa stvarnim brojevima i određenog stepena odustajanja i mišljenja da je taj broj jednostavno preteško precizno proceniti. Iako je teško utvrditi konačan broj, glavni razlog za odstupanje u procenama je nedostatak standardizovanih definicija šta znači prihvatanje Bitcoin-a.
Istina je da postoje različiti nivoi prihvatanja Bitcoin-a. Podelom na segmente prihvatanja Bitcoin-a lakše je uvideti ne samo zašto postoji širok opseg procena, već i još važnije, koliko je još uvek rano za prihvatanje Bitcoin-a kao preferirane zalihe vrednosti.
U ove svrhe, hajde da podelimo u segmente prihvatanje Bitcoin-a na četiri različita „nivoa“:
1. Kežual amateri (prstom u vodi)
2. Alokatori 1% (stopalima u vodi)
3. Značajni vernici (do pojasa u vodi)
4. Bitcoin maximalisti (u vodi preko glave)
Pre nego što počnemo, potreban nam je imenilac. Mogli bismo da koristimo globalno stanovništvo, ali po mom mišljenju ovo daje loše rezultate. Ono što mi zaista procenjujemo je koji procenat sveta koji poseduje odredjeno bogatstvo za skladištenje u Bitcoin-u, je to i učinio. Prema podacima sa sajta Statista, 2,2 biliona ljudi na svetu poseduje najmanje 10k USD u neto vrednosti, što se čini kao razumna granica za zalihu koju žele da uskladište. Činjenica je da će siromašne zajednice takođe koristiti Bitcoin kao zalihu vrednosti i verovatno će iz njega izvući veću korist kao rezultat marginalnog pristupa tradicionalnoj bankarskoj infrastrukturi kao klijenti banaka sa „niskom vrednošću“. Međutim, u naše svrhe, jednostavno gledamo koliko je ljudi usvojilo Bitcoin među grupama sa značajnim bogatstvom za skladištenje, tako da će 2.2 biliona služiti kao naša puna potencijalna veličina tržišta.
1. Kežual amateri
Ovaj segment ljudi koji su prihvatili Bitcoin uključuje sve one koji imaju bilo koju količinu Bitcoin-a – vašeg prijatelja sa 20 USD BTC-a negde u nekom novčaniku ili vašu tetku koja se ne seća svoje Coinbase lozinke iz 2017. Po mom mišljenju, najveća zabuna oko broja ljudi koji su prihvatili Bitcoin nastaje zbog poistovećivanja „kežual amatera“ sa ljudima koji su u potpunosti prihvatili Bitcoin. Realnost je takva da ljudi ovog segmenta uglavnom samo eksperimentišu, bilo da bi stekli osećaj za ono o čemu svi pričaju, ili samo uložu nekoliko dolara u Bitcoin u nadi da će možda dobiti džekpot, kao što je slučaj sa greb-greb nagradnim igrama.
Zbog toga, „kežual amateri“ su razlog dovodjenja u zabludu pravog broja ljudi koji su u potpunosti prihvatili Bitcoin. Njihovo ponašanje zapravo ne predstavlja prihvatanje u pravom smislu te reči i stoga se ne bi trebalo smatrati ljudima koji su u potpunosti prihvatili Bitcoin. Istina je da, kada kežual amateri shvate da je Bitcoin najbolja zaliha vrednosti neke imovine u istoriji, neće ostati na samo 20 USD u Bitcoin-ima. Umesto toga, oni će svoju štednju prebaciti u mnogo većim iznosima.
Što se tiče odredjivanja veličine ovog segmenta, Willy Woo je sastavio razumno iscrpnu i sveobuhvatnu procenu od oko 187 miliona ljudi koji su prihvatili Bitcoin, što znači da su oni u najmanju ruku „kežual amateri“.
Koristeći ovaj i naš puni potencijal od 2,2 biliona ljudi kao imenioca, 8,5% potencijalnih ljudi koji su prihvatili Bitcoin-e dostiglo je nivo „kežual amatera“. Ovo je prilično velik broj i potpuno obmanjuje stvarni obim potpunog prihvatanja, a što će pokazati sledeći segmenti.
2. Alokatori 1%
Za preostale potkategorije, tačni podaci su manje dostupni. Kao takvi, sve što možemo je da smislimo razumne procene putem triangulacije.
Po mom mišljenju, „alokatori 1%“ se mogu okarakterisati kao ljudi koji su prihvatili Bitcoin, i koji žele da imaju mali, ali ne i zanemarljivi deo u Bitcoin-u. Za naše svrhu, mislim da je pristojan prag za ovu grupu svako ko ima najmanje 0,1 Bitcoin, i može se smatrati da imaju malu, ali ne i zanemarljivu poziciju u Bitcoin-u.
Gledajući Bitcoin blockchain, postoji oko 3 miliona adresa koje imaju najmanje 0,1 BTC. Pored ovih brojeva na blockchain-u, moramo da uzmemo u obzir i znatan broj ljudi koji imaju ovaj iznos na berzi ili GBTC-u. Kombinovanjem, mislim da je razumno proceniti da je 10 miliona ljudi dostiglo nivo „alokatora 1%“ ili veći.
Na osnovu ovih brojeva, samo 1⁄17 „kežual amatera“ dostiglo je nivo prihvatanja „alokatora 1%“, što znači da je ovaj nivo prihvatanja Bitcoin-a do danas postigao samo 0,5% penetracije. Ovaj strmi pad je razlog zašto je došlo do zablude da veliki broj „kežual amatera“ bude označeno kao grupa koja je u potpunosti prihvatila Bitcoin.
3. Značajni vernici
U ovu kategoriju spada svako ko je dostigao nivo razumevanja Bitcoin-a da alokacija od 1% ili čak 5% više ne izgleda dovoljna.
Uopšteno govoreći, ova grupa se kreće u rasponu od 5 – 50%. Išao bih toliko daleko da bih rekao da je većina ljudi koji sebe smatraju vernicima u Bitcoin-e, uključujući većinu Bitcoin Twitter-a, negde u ovoj grupi.
Procena veličine ove grupe postaje mnogo nejasnija, ali možemo se osloniti na podatke iz blockchain-a da bismo došli do razumne procene.
Za početak, hajde da utvrdimo da je većina ljudi koji su dostigli ovaj nivo verovanja i razumevanja Bitcoin-a, izborila da poseduje najmanje 1 Bitcoin. Pored toga, ovaj nivo ljudi koji su prihvatili Bitcoin je verovatno osigurao svoj Bitcoin u chain-u novčanika kojim oni upravljaju. Gledajući podatke na chain-u, oko 820k adresa ima najmanje 1 Bitcoin. Kao grubu pretpostavku, uzmimo da 500k od toga poseduju ljudi koji su dostigli nivo prihvatanja „značajnog vernika“.
Ako potom generički zaokružimo akaunte za ljude koji nisu postigli status wholecoiner-a (eng. osoba koja poseduje barem 1 BTC), ili koji svoja sredstva drže na berzi, dolazimo do grube procene od 2 miliona „značajnih vernika“.
4. Bitcoin maximalisti
Za našu svrhu, recimo da ova grupa uključuje svakoga ko je dovoljno duboko ušao u Bitcoin da je zaključio da bi više od 50% njihove neto vrednosti trebalo da bude uskladišteno u Bitcoin-u.
Procena veličine ove grupe je gotovo nemoguća, zato ćemo morati da budemo kreativni.
-
Prodaja „Bitcoin Standard“
-
Hajde da konzervativno procenimo da je samo 20% maximalističara kupilo Bitcoin Standard, i da je 50% tih ljudi koji su ga razumeli, postali maksimalisti. Na osnovu knjige Amazon US rank (6,681), onlajn kalkulatori procenjuju da je prodato oko 15k primeraka.
- Hajde da budemo velikodušni i da zaokružimo taj broj od oko 15k na 50k, uzimajući u obzir međunarodnu prodaju i kupovinu izvan Amazona.
Ovo nas dovodi do procene broja od 125k maximalista. Da ne bismo pogrešili, bićemo oprezni, i udvostručimo taj broj i rećićemo da ih ima 250k.
- Kvalitativna triangulacija
Čisto subjektivno, ali čini mi se da na Twitter-u, primarnom domu za komunikaciju maximalista, postoji možda 10k aktivno angažovanih Bitcoin maximalista. Da budemo vrlo konzervativni, recimo da ovo predstavlja oko 5% maximalista (od ukupno 200k).
Uz to, kao procenu od vrha nadole, čini se opravdanim da je oko 10% ljudi koji su dostigli 5 – 50% alokacije Bitcoin-a napravilo skok ka maximalizmu.
Sve u svemu, cifra od oko 250k Bitcoin maximalista čini se konzervativnom, ako ne i velikodušnom pretpostavkom.
To nas dovodi do 0,01% penetracije.
Zaključak
Kako god gledali brojke, još uvek je rano za Bitcoin. Posmatrajući procenu vrednosti Bitcoin-a kao procenat njegovog punog potencijala, vidimo da je trenutna vrednost Bitcoin-a negde između 0,2% i 3% njegovog krajnjeg stanja, što znači da ostaje 30x do 500x rasta. Gledajući napredak prihvatanja Bitcoin-a, vidimo da je trenutna penetracija Bitcoin-a negde između 0,01% i 8,5%, u zavisnosti od toga koji prag prihvatanja gledate.
Ako verujete, kao što ja verujem, da je Bitcoin na putu da postane dominantna zaliha vrednosti i preferirani novac za ceo svet, na kraju će norma biti više od 50% posedovanja neto vrednosti u Bitcoin-u. Budući da naša analiza ovde sugeriše da samo 0,01% sveta zadovoljava ove standarde, opravdano je zaključiti da 99,99% sveta ostaje da sledi njihov primer.
Sve u svemu, dok svi koji se pojave na Bitcoin-u neizbežno osećaju žaljenje zbog toga što nisu ranije investirali i pitaju se da li su u potpunosti propustili brod, jasno je da većina rasta Bitcoin-a ostaje pred nama. Da stavimo ovo u neki kontekst, obzirom da može postojati samo 21 milion Bitcoin-a, prosečna osoba na zemlji (od 8 biliona ljudi) imaće samo 0,0025 Bitcoin-a. Još je toliko rano, da ukupna neto vrednost te prosečne osobe u Bitcoin-u može da se kupi za samo 90 USD.
I ako mislite da je kasno, zapravo je veoma rano, zato vam čestitam i uživajte u skupljanju sats-ova dok su još uvek ovako jeftini!
-
 @ 6be5cc06:5259daf0
2025-05-27 20:37:22
@ 6be5cc06:5259daf0
2025-05-27 20:37:22At
até uma ferramenta de agendamento de tarefas em Linux usada para executar comandos únicos em um horário e data específicos. Diferente docron, que serve para tarefas recorrentes, oatexecuta uma única vez.Como usar o
at1. Verifique se o
atestá instaladobash which atSe não estiver instalado:
bash sudo apt install atE inicie o serviço (caso necessário):
bash sudo systemctl enable --now atd2. Agendar um comando
bash at 10:00 AM tomorrowVocê será levado a um prompt interativo. Digite o comando desejado e finalize com
Ctrl + D.Exemplo 1:
bash at 09:00 AM next Monday(Entrada do usuário no prompt do
at)echo "Relatório pronto" >> ~/relatorio.txt Ctrl + DResultado: O trecho "relatório pronto" será incluído no documento relatorio.txt.
Exemplo 2:
bash at 21:00 Apr 15Entrada no prompt:
notify-send "Hora de fazer backup!" Ctrl + DResultado: Às 21h do dia 15 de abril, o sistema exibirá uma notificação.
Formatos de Data e Hora Válidos
-
now + 1 minute -
midnight -
tomorrow -
5pm -
08:30 -
7:00am next friday -
noon + 2 days
Visualizar tarefas agendadas
bash atqRemover uma tarefa agendada
bash atrm <número_da_tarefa>Você encontra o número da tarefa com
atq.
cron
O
croné um utilitário de agendamento de tarefas baseado no tempo. Permite executar comandos ou scripts automaticamente em horários específicos. Ele depende do daemoncrond, que deve estar ativo e em execução contínua no sistema.Arquivo de configuração:
-
Cada usuário pode editar seu próprio agendador com:
bash crontab -e -
O formato padrão de uma linha no crontab:
m h dom mon dow comando
|Campo|Descrição|Valores possíveis| |---|---|---| |m|Minuto|0–59| |h|Hora|0–23| |dom|Dia do mês|1–31| |mon|Mês|1–12| |dow|Dia da semana|0–6 (0 = Domingo)| |comando|Comando a executar|Qualquer comando shell válido|
Exemplos:
-
Executar um script a cada minuto:
bash * * * * * /usr/local/bin/execute/this/script.sh -
Fazer backup no dia 10 de junho às 08:30:
bash 30 08 10 06 * /home/sysadmin/full-backup -
Backup todo domingo às 5h da manhã:
bash 0 5 * * 0 tar -zcf /var/backups/home.tgz /home/
Limitações:
Tarefas agendadas com
cronnão são executadas se o computador estiver desligado ou suspenso no horário programado. O comando é simplesmente ignorado. Usecronpara tarefas com data/hora exatas.
anacron
O
anacroné uma alternativa aocronvoltada para sistemas que não ficam ligados o tempo todo, como notebooks e desktops. Ele garante a execução de tarefas periódicas (diárias, semanais, mensais) assim que possível após o sistema ser ligado, caso tenham sido perdidas. Useanacronpara tarefas periódicas tolerantes a atrasos.Verificação da instalação:
bash anacron -VInstalação (caso necessário):
bash sudo apt update sudo apt install anacronArquivo de configuração:
/etc/anacrontabAcessado com:
sudo nano /etc/anacrontabFormato de cada linha:
PERIOD DELAY IDENT COMMAND| Campo | Descrição | | ------- | ------------------------------------------- | | PERIOD | Intervalo em dias (1 = diário, 7 = semanal) | | DELAY | Minutos a esperar após o boot | | IDENT | Nome identificador da tarefa | | COMMAND | Comando ou script a ser executado |
Exemplo:
bash 1 3 limpeza-temporarios /home/usuario/scripts/limpar_tmp.shExecuta o script uma vez por dia, 3 minutos após o sistema ser ligado.
Nota: Não é necessário usar
run-partsnemcron.dailypara tarefas personalizadas. Basta apontar diretamente para o script desejado. Orun-partssó deve ser usado quando se deseja executar todos os scripts de um diretório.Ativação do serviço:
bash sudo systemctl enable --now anacronVerificação de status:
bash systemctl status anacronLogs de execução:
bash grep anacron /var/log/syslog/etc/anacrontab: Arquivo de Configuração doanacronO arquivo
/etc/anacrontabdefine tarefas periódicas a serem executadas peloanacron, garantindo que comandos sejam executados mesmo que o computador esteja desligado no horário originalmente programado.Cabeçalho Padrão
bash SHELL=/bin/sh HOME=/root LOGNAME=root-
SHELL: Shell padrão utilizado para executar os comandos. -
HOME: Diretório home usado durante a execução. -
LOGNAME: Usuário associado à execução das tarefas.
Entradas Padrão do Sistema
bash 1 5 cron.daily run-parts --report /etc/cron.daily 7 10 cron.weekly run-parts --report /etc/cron.weekly @monthly 15 cron.monthly run-parts --report /etc/cron.monthly|Campo|Significado| |---|---| |
1|Executa a tarefa diariamente (a cada 1 dia)| |5|Espera 5 minutos após o boot| |cron.daily|Identificador da tarefa (usado nos logs)| |run-parts|Executa todos os scripts dentro do diretório|Diretórios utilizados:
-
/etc/cron.daily: scripts executados uma vez por dia -
/etc/cron.weekly: scripts semanais -
/etc/cron.monthly: scripts mensais
O comando
run-partsexecuta automaticamente todos os scripts executáveis localizados nesses diretórios.Personalização
Para adicionar tarefas personalizadas ao
anacron, basta adicionar novas linhas com o formato:PERIOD DELAY IDENT COMMANDExemplo:
bash 1 3 limpeza-temporarios /home/usuario/scripts/limpar_tmp.shExecuta o script
limpar_tmp.shdiariamente, com 3 minutos de atraso após o boot.Importante: Não é necessário — nem recomendado — usar
run-partsquando a intenção é executar um script individual. Orun-partsespera um diretório e ignora arquivos individuais. Usarrun-partscom um script individual causará falha na execução. -
-
 @ bf47c19e:c3d2573b
2025-05-27 20:23:48
@ bf47c19e:c3d2573b
2025-05-27 20:23:48Originalni tekst na bitcoin-balkan.com.
Pregled sadržaja
- Šta je Bitcoin?
- Šta Bitcoin može da učini za vas?
- Zašto ljudi kupuju Bitcoin?
- Da li je vaš novac siguran u dolarima, kućama, akcijama ili zlatu?
- Šta je bolje za štednju od dolara, kuća i akcija?
- Po čemu se Bitcoin razlikuje od ostalih valuta?
- kako Bitcoin spašava svet?
- Kako mogu da saznam više o Bitcoin-u?
Bitcoin čini da štednja novca bude kul – i praktična – ponovo. Ovaj članak objašnjava kako i zašto.
Šta je Bitcoin?
Bitcoin se naziva digitalno zlato, mašina za istinu, blockchain, peer to peer mreža čvorova, energetski ponor i još mnogo toga. Bitcoin je, u stvari, sve ovo. Međutim, ova objašnjenja su često toliko tehnička i suvoparna, da bi većina ljudi radije gledala kako trava raste. Što je najvažnije, ova objašnjenja ne pokazuju kako Bitcoin ima bilo kakve koristi za vas.
iPod nije postao kulturološka senzacija jer ga je Apple nazvao „prenosnim digitalnim medijskim uređajem“. Postao je senzacija jer su ga zvali “1,000 pesama u vašem džepu.”
Ne zanima vas šta je Bitcoin. Vas zanima šta on može da učini za vas.
Baš kao i Internet, vaš auto, vaš telefon, kao i mnogi drugi uređaji i sistemi koje svakodnevno koristite, vi ne treba da znate šta je Bitcoin ili kako to funkcioniše da biste razumeli šta on može da učini za vas.
Šta Bitcoin može da učini za vas?
Bitcoin može da sačuva vaš teško zarađeni novac.
Bitcoin je stekao veliku pažnju u 2017. i 2018. godini zbog svoje spekulativne upotrebe. Mnogi ljudi su ga kupili nadajući se da će se obogatiti. Cena je naglo porasla, a zatim se srušila. Ovo nije bio prvi put da je Bitcoin uradio to. Međutim, niko nikada nije izgubio novac držeći bitcoin duže od 3,5 godine – ćak i ako je kupio na apsolutnim vrhovima.
Zašto Bitcoin konstantno raste? Ljudi počinju da shvataju koliko je Bitcoin moćan, kao način uštede novca u svetu u kojem je ’novac’ poput dolara, eura i drugih nacionalnih valuta dizajniran da gubi vrednost.
Ovo čini Bitcoin odličnom opcijom za štednju novca na nekoliko godina ili više. Bitcoin je bolji od štednje novca u dolarima, akcijama, nekretninama, pa čak i u zlatu.
Zato pokušajte da zaboravite na trenutak na razumevanje blockchaina, digitalne valute, kriptografije, seed fraza, novčanika, rudarstva i svih ostalih nerazumljivih termina. Za sada, razgovarajmo o tome zašto ljudi kupuju Bitcoin: razlog je prostiji nego što vi mislite.
Zašto ljudi kupuju Bitcoin?
Naravno, svako ima svoj razlog za kupovinu Bitcoin-a. Jedan od razloga, koji verovatno često čujete, je taj što mu vrednost raste. Ljudi žele da se obogate. Uskoče kao spekulanti, krenu u vožnju i najverovatnije ih prodaju ubrzo nakon kupovine.
Međutim, čak i kada cena krene naglo prema gore i strmoglavo padne nazad, mnogi ljudi ostanu i nakon tog pada. Otkud mi to znamo? Broj aktivnih novčanika dnevno, koji je otprilike sličan broju korisnika Bitcoin-a, nastavlja da raste. Takođe, nakon svakog balona u istoriji Bitcoin-a, cena se nikada ne vraća na svoju cenu pre balona. Uvek ostane malo višlja. Bitcoin se penje, a svaka masovna spekulativna serija dovodi sve više i više ljudi.
Broj aktivnih Bitcoin novčanika neprekidno raste
„Aktivna adresa“ znači da je neko tog dana poslao Bitcoin transakciju. Donji grafikon je na logaritamskoj skali.
 Izvor: Glassnode
Izvor: GlassnodeCena Bitcoina se neprestano penje
Kroz istoriju Bitcoin-a možemo videti divlje kolebanje cena, ali nakon svakog balona, cena se ostaje višlja nego pre. Ovo je cena Bitcoin-a na logaritamskoj skali.
 Izvor: Glassnode
Izvor: GlassnodeTo pokazuje da se ljudi zadržavaju: potražnja za Bitcoin-om se povećava. Da je svaki masovni rast cena bio samo balon koji su iscenirali prevaranti koji žele brzo da se obogate, cena bi se vratila na nivo pre balona. To se dogodilo sa lalama, ali ne i sa Bitcoin-om.
I zašto se onda cena Bitcoin-a stalno povećava? Sve veći broj ljudi čuva Bitcoin dugoročno – oni razumeju šta Bitcoin može učiniti za njihovu štednju.
Zašto ljudi štede svoj novac u Bitcoin-u umesto na štednim računima, kućama, deonicama ili zlatu? Hajde da pogledajmo sve te metode štednje, i zatim da ih uporedimo sa Bitcoin-om.
Da li je vaš novac siguran u dolarima, kućama, akcijama ili zlatu?
Tokom mnogo godina, to su bile pristojne opcije za štednju. Međutim, sistem koji podržava vrednost svega ovoga je u krizi.
Dolari, Euri, Dinari
Dolari i sve ostale „tradicionalne“ valute koje proizvode vlade, stvorene su da izgube vrednost kroz inflaciju. Banke i tradicionalni monetarni sistem uzrokuju inflaciju stalnim stvaranjem i distribucijom novog novca. Kada Američke Federalne Rezerve objave ciljanu stopu od 2% inflacije, to znači da žele da vaš novac svake godine izgubi 2% od svoje vrednosti. Čak i sa inflacijom od samo 2%, vaša štednja u dolarima izgubiće polovinu vrednosti tokom 40-godišnjeg radnog veka.
Izveštena inflacija se danas opasno povečava, uprkos rastućem „buretu sa barutom“ koji bi mogao da explodira i dovede do masivne hiperinflacije. Što je više valute u opticaju, to je više baruta u buretu.
Naše vlade su ekonomiju napunile valutama da bankarski sistem ne bi propao nakon finansijske krize koja se dogodila 2008. godine. Od tada je većina glavnih centralnih banaka postavila vrlo niske kamatne stope, što pojedincima i korporacijama omogućava dobijanje jeftinijih kredita. To znači da mnogi pojedinci i korporacije podižu ogromne kredite i koriste ih za kupovinu druge imovine poput deonica, umetničkih dela i nekretnina. Sve ovo pozajmljivanje znači da stvaramo tone novog novca i stavljamo ga u opticaj.
Računi za podsticaje (stimulus bills) COVID-19 za 2020. godinu unose trilione u sistem. Ovoliko stvaranje valuta na kraju dovodi do inflacije – velikog gubitka u vrednosti valute.
 Količina američkog dolara u opticaju gotovo se udvostručila od marta 2020. godine. Izvor
Količina američkog dolara u opticaju gotovo se udvostručila od marta 2020. godine. IzvorRačuni za podsticaje su bez presedana, toliko da je neko izmislio meme da opiše ovu situaciju.
Resurs koji vlade mogu da naprave u većem broju da bi platile svoje račune? Ne zvuči kao dobro mesto za štednju novca.
Kuće
Kuće su tokom prošlog veka bile pristojan način štednje novca. Međutim, pad cena nekretnina 2007. godine doveo je do toga da su mnogi vlasnici kuća izgubili svu ušteđevinu.
Danas su kuće gotovo nepristupačne za prosečnog čoveka. Jedan od načina da se ovo izmeri je koliko godišnjih zarada treba prosečnom čoveku da zaradi ekvivalent vrednosti prosečne kuće. Prema CityLab-u, publikaciji Bloomberg-a koja pokriva gradove, porodica može da priuštiti određenu kuću ako košta manje od 2,6 godišnjih prihoda domaćinstva te porodice.
Međutim, prema RZS (Republički zavod za statistiku) prosečan prihod porodičnog domaćinstva u Srbiji iznosi oko 570 EUR mesečno ili otprilike 7.000 EUR godišnje. Nažalost, samo najjeftinija područja van gradova imaju srednje cene kuća od oko 2,6 prosečnih godišnjih prihoda domaćinstva. U većim gradovima poput Beograda i Novog Sada srednja cena kuće je veća od 10 prosečnih godišnjih prihoda jednog domaćinstva.
Ako nekako možete sebi da priuštite kuću, ona bi mogla biti pristojna zaliha vrednosti. Dokle god ne doživimo još jedan krah i izvršitelji zaplene ovu imovinu mnogim vlasnicima kuća.
Akcije
Berza je u prošlosti takođe dobro poslovala. Međutim, sporo i stabilno povećanje tržišta događa se u dosadnom, predvidljivom svetu. Svakog dana vidimo sve manje toga. Nakon ubrzanja korona virusa, videli smo smo najbrži pad američke berze u istoriji od 25% – brži od Velike depresije.
Neki se odlučuju za ulaganje u obveznice i drugu finansijsku imovinu, ali ’prinosi’ za tu imovinu – procenat kamate zarađene na imovinu iz godine u godinu – stalno opada. Sve veći broj odredjenih imovina ima čak i negativne prinose, što znači da posedovanje te imovine košta! Ovo je veliki problem za sve koji se oslanjaju na penziju. Plus, s obzirom na to da su akcije denominovane u tradicionalnim valutama poput dolara i evra, inflacija pojede prinos koji investitor dobije.
Najgore od svega je to što ti isti ekonomski krahovi koji uzrokuju masovna otpuštanja i teško tržište rada takođe znače i nagli pad cena akcija. Čuvanje ušteđevine u akcijama može značiti i gubitak štednje i gubitak posla zbog recesije. Teška vremena mogu da vas prisile da svoje akcije prodate po vrlo malim cenama samo da biste platili svoje račune.
A to nije baš siguran način štednje novca.
Zlato
Vrednost zlata neprekidno se povećavala tokom 5000 godina, obično padajući onda kada berza obećava jače prinose.
Evidencija vrednosti zlata je solidna. Međutim, zlato nosi i druge rizike. Većina ljudi poseduje zlato na papiru. Oni fizički ne poseduju zlato, već ga njihova banka čuva za njih. Zbog toga je zlato veoma podložno konfiskaciji od strane vlade.
Zašto bi vlada konfiskovala nečije zlato, a kamoli u demokratskoj zemlji u „slobodnom svetu“? Ali to se dešavalo i ranije. 1933. godine Izvršnom Naredbom 6102, predsednik Roosevelt naredio je svim Amerikancima da prodaju svoje zlato vladi u zamenu za papirne dolare. Vlada je iskoristila pretnju zatvorom za prikupljanje zlata u fizičkom obliku. Znali su da se zlato više poštuje kao zaliha vrednosti širom sveta od papirnih dolara.
Ako posedujete svoje zlato na nekoj od aplikacija za trgovanje akcijama, možete se kladiti da će vam ga država oduzeti ako joj zatreba. Čak i ako posedujete fizičko zlato, onda ga izlažete mogućnosti krađe – od strane kriminalca ili vaše vlade.
Vaša uštedjevina nije bezbedna.
Rast cena svih gore navedenih sredstava zavisi od našeg trenutnog političkog i ekonomskog sistema koji se nastavlja kao i tokom proteklih 100 godina. Međutim, danas vidimo ogromne pukotine u ovom sistemu.
Sistem ne funkcioniše dobro za većinu ljudi.
Od 1971. plate većine američkih radnika nisu rasle. S druge strane, bogatstvo koje imaju najbogatiji u društvu nalazi se na nivoima koji nisu viđeni više od 80 godina. U međuvremenu, ljudi sve manje i manje veruju institucijama poput banaka i vlada.
 CBPP Nejednakost Bogatstva Tokom Vremena
CBPP Nejednakost Bogatstva Tokom VremenaŠirom sveta možemo videti dokaze o slamanju sistema kroz politički ekstremizam: izbor Trampa i drugih ekstremističkih desničarskih kandidata, Bregzit, pokret Occupy, popularizacija koncepta univerzalnog osnovnog dohotka, povratak pojma „socijalizam“ nazad u modu. Ljudi na svim delovima političkog i društvenog spektra osećaju problematična vremena i posežu za sve radikalnijim rešenjima.
Šta je bolje za štednju od dolara, kuća i akcija?
Pa kako ljudi mogu da štede novac u ovim teškim vremenima? Ili ne koriste tradicionalne valute, ili kupuju sredstva koja će zadržati vrednost u teškim vremenima.
Bitcoin ima najviše potencijala da zadrži vrednost kroz politička i ekonomska previranja od bilo koje druge imovine. Na tom putu će biti rupa na kojima će se rušiti ili pumpati, međutim, njegova svojstva čine ga takvim da će verovatno preživeti previranja kada druga imovina ne bude to mogla.
Šta Bitcoin čini drugačijim?
Bitcoini su retki.
Proces ‘rudarenja’ bitcoin-a, proizvodnju bitcoin-a čini veoma skupom, a Bitcoin protokol ograničava ukupan broj bitcoin-a na 21 milion novčića. To čini Bitcoin imunim na nagle poraste ponude. Ovo se veoma razlikuje od tradicionalnih valuta, koje vlade mogu da štampaju sve više kad god one to požele. Zapamtite, povećanje ponude vrši veliki pritisak na vrednost valute.
Bitcoini nemaju drugu ugovornu stranu.
Bitcoin se takođe razlikuje od imovine kao što su obveznice, akcije i kuće, jer mu nedostaje druga ugovorna strana. Druge ugovorne strane su drugi subjekti uključeni u vrednost sredstva, koji to sredstvo mogu obezvrediti ili vam ga uzeti. Ako imate hipoteku na svojoj kući, banka je druga ugovorna strana. Kada sledeći put dođe do velikog finansijskog kraha, banka vam može oduzeti kuću. Kompanije su kvazi-ugovorne strane akcijama i obveznicama, jer mogu da počnu da donose loše odluke koje utiču na njihovu cenu akcija ili na „neizvršenje“ duga (da ga ne vraćaju vama ili drugim poveriocima). Bitcoin nema ovih problema.
Bitcoin je pristupačan.
Svako sa 5 eura i mobilnim telefonom može da kupi i poseduje mali deo bitcoin-a. Važno je da znate da ne morate da kupite ceo bitcoin. Bitcoin-i su deljivi do 100-milionite jedinice, tako da možete da kupite Bitcoin u vrednosti od samo nekoliko eura. Neuporedivo lakše nego kupovina kuće, zlata ili akcija!
Bitcoin se ne može konfiskovati.
Banke drže većinu vaših eura, zlata i akcija za vas. Većina ljudi u razvijenom svetu veruje bankama, jer većina ljudi koji žive u današnje vreme nikada nije doživela konfiskaciju imovine ili ’šišanje’ od strane banaka ili vlada. Nažalost, postoji presedan za konfiskaciju imovine čak i u demokratskim zemljama sa snažnom vladavinom prava.
Kada vlada konfiskuje imovinu, ona obično ubedi javnost da će je menjati za imovinu jednake vrednosti. U SAD-u 1930-ih, vlada je davala dolare vlasnicima zlata. Vlada je znala da uvek može da odštampa još više dolara, ali da ne može da napravi više zlata. Na Kipru 2012. godine, jedna propala banka je svojim klijentima dala deonice banke da pokrije dolare klijenata koje je banka trebala da ima. I dolari i deonice su strmoglavo opali u odnosu na imovinu koja je uzeta od ovih ljudi.
Doći do bitcoin-a koji ljudi poseduju, biće mnogo teže jer se bitcoin-i mogu čuvati u novčaniku koji ne poseduje neka treća strana, a vi možete čak i da zapamtite privatne ključeve do vašeg bitcoin-a u glavi.
Bitcoin je za štednju.
Bitcoin se polako pokazuje kao najbolja opcija za dugoročnu štednju novca, posebno s obzirom na današnju ekonomsku klimu. Posedovanje čak i malog dela, je polisa osiguranja koja se isplati ako svet i dalje nastavi da ludi. Cena Bitcoin-a u dolarima može divlje da varira u roku od godinu ili dve, ali tokom 3+ godine skoro svi vide slične ili više cene od trenutka kada su ga kupili. U stvari, doslovno niko nije izgubio novac čuvajući Bitcoin duže od 3,5 godine – čak i ako je kupio BTC na apsolutnim vrhovima tržišta.

Imajte na umu da nakon ove tačke ti ljudi više nikada nisu videli rizik od gubitka. Cena se nikada nije smanjila niže od najviše cene u prethodnom ciklusu.
Po čemu se Bitcoin razlikuje od ostalih valuta?
Bitcoin funkcioniše tako dobro kao način štednje zbog svog neobičnog dizajna, koji ga čini drugačijim od bilo kog drugog oblika novca koji je postojao pre njega. Bitcoin je digitalna valuta, prvi i verovatno jedini primer valute koja ima ograničenu ponudu dok radi na otvorenom, decentralizovanom sistemu. Vlade strogo kontrolišu valute koje danas koristimo, poput dolara i eura, i proizvode ih za finansiranje ratova i dugova. Korisnici Bitcoin-a – poput vas – kontrolišu Bitcoin protokol.
Evo šta Bitcoin razlikuje od dolara, eura i drugih valuta:
Bitcoin je otvoren sistem.
Svako može da odluči da se pridruži Bitcoin mreži i primeni pravila softverskog protokola, što je dovelo do vrlo decentralizovanog sistema u kojem nijedan pojedinac ili entitet ne može da blokira transakciju, zamrzne sredstva ili da ukrade od druge osobe.Današnji savremeni bankarski sistem se uveliko razlikuje. Nekoliko banaka je dobilo poverenje da gotovo sve valute, akcije i druge vredne predmete čuvaju na “sigurnom” za svoje klijente. Da biste postali banka, potrebni su vam milioni dolara i neverovatne količine političkog uticaja. Da biste pokrenuli Bitcoin čvor i postali „svoja banka“, potrebno vam je nekoliko stotina dolara i jedno slobodno popodne.
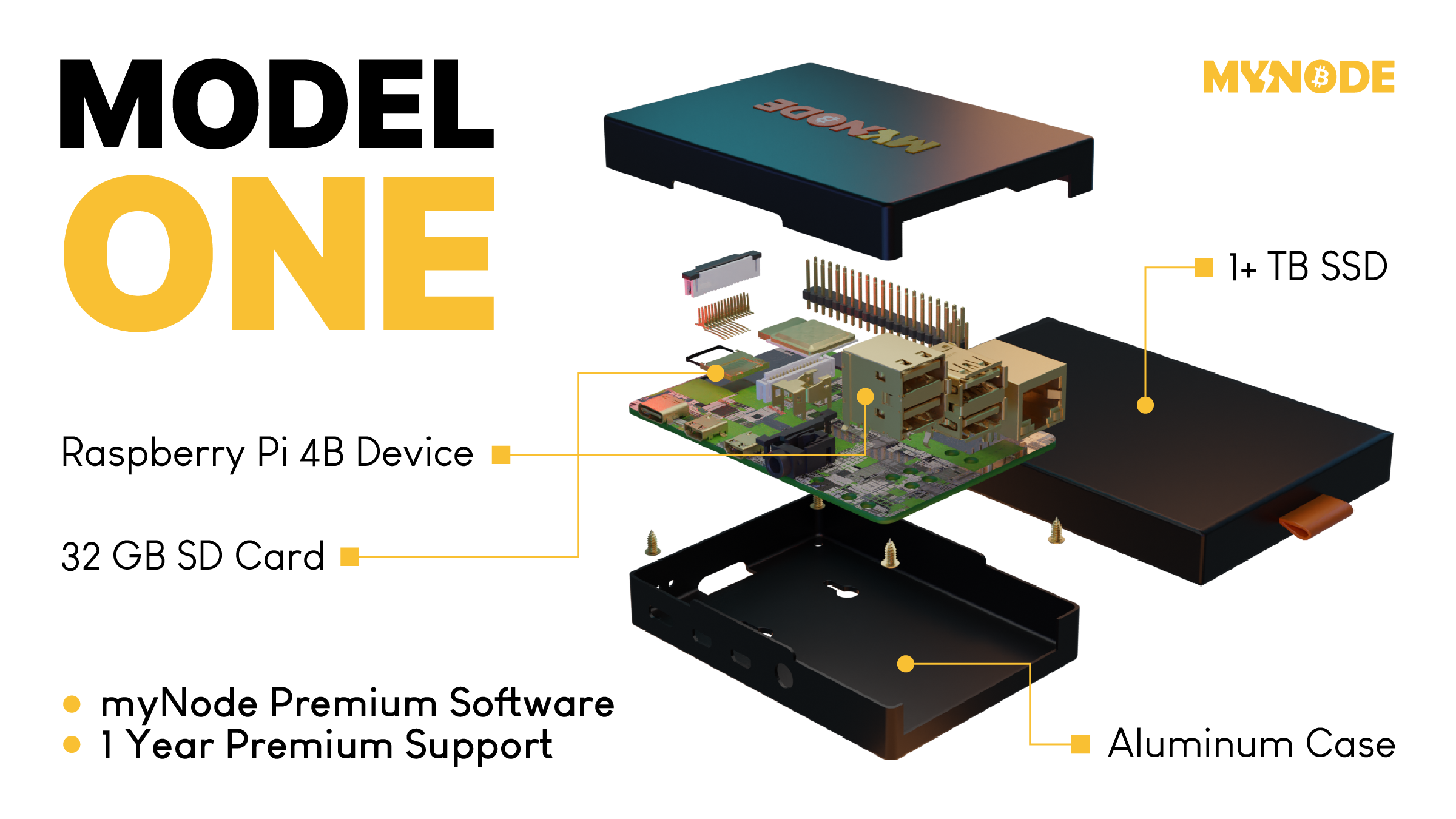 Tako izgleda Bitcoin čvor – Node
MyNode čvor vam omogućava da postanete svoja banka za samo nekoliko minuta.
Tako izgleda Bitcoin čvor – Node
MyNode čvor vam omogućava da postanete svoja banka za samo nekoliko minuta.Bitcoin ima ograničenu ponudu.
Softverski protokol otvorenog koda koji upravlja Bitcoin sistemom ograničava broj novih bitcoin-a koji se mogu stvoriti tokom vremena, sa ograničenjem od ukupno 21.000.000 bitcoin-a. S druge strane, valute koje danas koristimo imaju neograničenu ponudu. Istorija i sadašnje odluke centralnih banaka govore nam da će vlade uvek štampati sve više i više valuta, sve dok valuta ne bude bezvredna. Sve ovo štampanje uzrokuje inflaciju, što pravi štetu običnim radnim ljudima i štedišama.
Tradicionalne valute su dizajnirane tako da opadaju vremenom. Svaki put kada centralna banka kaže da cilja određenu stopu inflacije, oni ustvari kažu da žele da vaš novac svake godine izgubi određeni procenat svoje vrednosti.
Bitcoin-ova ograničena ponuda znači da je on tako dizajniran da raste vremenom kako se potražnja za njim povećava.

Bitcoin putuje oko sveta za nekoliko minuta.
Svako može da pošalje bitcoin-e za nekoliko minuta širom sveta, bez obzira na granice, banke i vlade. Potrebno je manje od minuta da se transakcija pojavi na novčaniku primaoca i oko 60 minuta da se transakcija u potpunosti „obračuna“, tako da primaoc može da bude siguran da su primljeni bitcoin-i sada njegovi (6 konfirmacija bloka). Slanje drugih valuta širom sveta traje danima ili čak mesecima ako se šalju milionski iznosi, a podrazumeva i visoke naknade.
Neke vlade i novinari tvrde da ova sloboda putovanja koju pruža Bitcoin pomaže kriminalcima i teroristima. Međutim, transakciju Bitcoin-a je lakše pratiti nego većinu transakcija u dolarima ili eurima.
Bitcoin se može čuvati na “USB-u”.
Dizajn Bitcoin-a je takav da vam treba samo da čuvate privatni ključ do svojih ‘bitcoin’ adresa (poput lozinke do bankovnih računa) da biste pristupili svojim bitcoin-ima odakle god poželite. Ovaj privatni ključ možete da sačuvate na disku ili na papiru u obliku 12 ili 24 reči na engleskom jeziku. Kao rezultat toga, možete da držite Bitcoin-e vredne milione dolara u svojoj šaci.
Sve ostale valute danas možete ili da strpate u svoj dušek ili da ih poverite banci na čuvanje. Za većinu ljudi koji žive u razvijenom svetu, i koji ne osporavaju autoritet i poverenje u banku, ovo deluje sasvim dobro. Međutim, oni kojima je potrebno da pobegnu od ugnjetavačke vlade ili koji naljute pogrešne ljude, ne mogu verovati bankama. Za njih je sposobnost da nose svoju ušteđevinu bez potrebe za ogromnim koferom neprocenjiva. Čak i ako ne živite na mestu poput ovog, cena Bitcoin-a se i dalje povećava kada ih neko kome oni trebaju kupi.
Kako Bitcoin spašava svet?
Bitcoin, kao ultimativni način štednje, je cakum pakum, ali da li on pomaže u poboljšanju sveta u celini?
Kao što ćete početi da shvatate, ulazeći sve dublje i u druge sadržaje na ovoj stranici, mnogi temeljni delovi našeg današnjeg monetarnog sistema i ekonomije su duboko slomljeni. Međutim, oni koji upravljaju imaju korist od ovakvih sistema, pa se on verovatno neće promeniti bez revolucije ili mirnog svrgavanja od strane naroda. Bitcoin predstavlja novi sistem, sa nekoliko glavnih prednosti:
- Bitcoin popravlja novac, koji je milenijumima služio kao važan alat za rast i poboljšanje društva.
- Bitcoin vraća zdrav razum pozajmljivanju, uklanjanjem apsurdnih situacija poput negativnih kamatnih stopa (gde zajmitelj plaća da bi se zadužio).
- Bitcoin pokreće ulaganja u obnovljive izvore energije i poboljšava energetsku efikasnost u mreži, služeći kao „krajnji kupac“ za sve vrste energije.
Kako mogu da saznam više o Bitcoin-u?
Ovaj članak vam je dao osnovno razumevanje zašto biste trebali razmišljati o Bitcoin-u. Ako želite da saznate više, preporučujem ove resurse:
- Film "Bitcoin: Kraj Novca Kakav Poznajemo"
- Još uvek je rano za Bitcoin
- Zasto baš Bitcoin?
- Šta je to Bitcoin?
- The Bitcoin Whitepaper ← objavljen 2008. godine, ovo je izložio dizajn za Bitcoin.
-
 @ eb0157af:77ab6c55
2025-05-28 12:01:31
@ eb0157af:77ab6c55
2025-05-28 12:01:31A fake Uber driver steals $73,000 in XRP and $50,000 in Bitcoin after drugging an American tourist.
A U.S. citizen vacationing in the United Kingdom fell victim to a scam that cost him $123,000 in cryptocurrencies stored on his smartphone. The man was drugged by an individual posing as an Uber driver.
According to My London, Jacob Irwin-Cline had spent the evening at a London nightclub, consuming several alcoholic drinks before requesting an Uber ride home. The victim admitted he hadn’t carefully verified the booking details on his device, mistakenly getting into a private taxi driven by someone who, at first glance, resembled the expected Uber driver but was using a completely different vehicle.
Once inside the car, the American tourist reported that the driver offered him a cigarette, allegedly laced with scopolamine — a rare and powerful sedative. Irwin-Cline described how the smoke made him extremely docile and fatigued, causing him to lose consciousness for around half an hour.
Upon waking, the driver ordered the victim to get out of the vehicle. As Irwin-Cline stepped out, the man suddenly accelerated, running him over and fleeing with his mobile phone, which contained the private keys and access to his cryptocurrencies. Screenshots provided to MyLondon show that $73,000 worth of XRP and $50,000 in bitcoin had been transferred to various wallets.
This incident adds to a growing trend of kidnappings, extortions, armed robberies, and ransom attempts targeting crypto executives, investors, and their families.
Just a few weeks ago, the daughter and grandson of Pierre Noizat, CEO of crypto exchange Paymium, were targeted in a kidnapping attempt in Paris. The incident took place in broad daylight when attackers tried to force the family into a parked vehicle. However, Noizat’s daughter managed to fight off the assailants.
The post American tourist drugged and robbed: $123,000 in crypto stolen in London appeared first on Atlas21.
-
 @ cae03c48:2a7d6671
2025-05-28 12:00:44
@ cae03c48:2a7d6671
2025-05-28 12:00:44Bitcoin Magazine

President Trump Supports Strategic Bitcoin Reserve Bill, Senator Lummis SaysToday at the Bitcoin 2025 Conference in Las Vegas, Nevada, US Senator Cynthia Lummis of Wyoming, Senator Marsha Blackburn of Tennessee, and Senator Jim Justice of West Virginia, took the stage to give updates on federal and state level Bitcoin adoption in the United States.
JUST IN:
 Senator Cynthia Lummis said US military generals are "big supporters" of a Strategic Bitcoin Reserve for economic power. pic.twitter.com/2RPMV3tbdA
Senator Cynthia Lummis said US military generals are "big supporters" of a Strategic Bitcoin Reserve for economic power. pic.twitter.com/2RPMV3tbdA— Bitcoin Magazine (@BitcoinMagazine) May 27, 2025
Cynthia Lummis announced that President Donald Trump is supportive of her Strategic Bitcoin Reserve Act, which would see the United States purchase 1,000,000 BTC, among other pro-Bitcoin and stablecoin legislation.
“President Trump supports the bill,” she stated. “And he has a team in the White House working on digital assets — everything from stablecoins to market structure to Bitcoin Strategic Reserve. And they will probably roll out in that order.”
“States have always been the incubators of innovation,” Lummis said. “Senator Justice was the Governor of West Virginia, Senator Blackburn will be the next Governor of Tennessee. The states are where the innovation is occurring.”
“So you have Arizona, Texas and New Hampshire that passed Strategic Bitcoin Reserve bills this year,” she continued. “30 states consider Strategic Bitcoin Reserves. We have the United Arab Emirates purchasing Bitcoin through American exchange traded funds — that’s good for America.”

Senator Blackburn echoed Lummis’ statements, sharing her thoughts on how other countries will follow the United States in their adoption of Bitcoin.
“Many of our allies follow what we do,” Blackburn said. “Everybody wants to be a part of of our market, they want to be a part of our trade. And they will follow what we do. And as Senator Lummis said, we already see countries that are establishing these reserves. So it is vitally important that we hold this as a portion of our reserves.”
Justice emphasized that to be successful, “we have got to get the economics right. Many people ask me many times as Governor, ‘what’s the most important thing you do?’ And I’ll promise you this, it’s all about the economics.”
Justice then went on to explain that when the average, everyday person is using Bitcoin to purchase their necessities, that legislation will start “happening at light speed”, because politicians want to get re-elected and therefore must follow the will of the people.

You can watch the full panel discussion and the rest of the Bitcoin 2025 Conference Industry Day below:
This post President Trump Supports Strategic Bitcoin Reserve Bill, Senator Lummis Says first appeared on Bitcoin Magazine and is written by Nik.
-
 @ af9c48b7:a3f7aaf4
2024-11-18 20:26:07
@ af9c48b7:a3f7aaf4
2024-11-18 20:26:07Chef's notes
This simple, easy, no bake desert will surely be the it at you next family gathering. You can keep it a secret or share it with the crowd that this is a healthy alternative to normal pie. I think everyone will be amazed at how good it really is.
Details
- ⏲️ Prep time: 30
- 🍳 Cook time: 0
- 🍽️ Servings: 8
Ingredients
- 1/3 cup of Heavy Cream- 0g sugar, 5.5g carbohydrates
- 3/4 cup of Half and Half- 6g sugar, 3g carbohydrates
- 4oz Sugar Free Cool Whip (1/2 small container) - 0g sugar, 37.5g carbohydrates
- 1.5oz box (small box) of Sugar Free Instant Chocolate Pudding- 0g sugar, 32g carbohydrates
- 1 Pecan Pie Crust- 24g sugar, 72g carbohydrates
Directions
- The total pie has 30g of sugar and 149.50g of carboydrates. So if you cut the pie into 8 equal slices, that would come to 3.75g of sugar and 18.69g carbohydrates per slice. If you decided to not eat the crust, your sugar intake would be .75 gram per slice and the carborytrates would be 9.69g per slice. Based on your objective, you could use only heavy whipping cream and no half and half to further reduce your sugar intake.
- Mix all wet ingredients and the instant pudding until thoroughly mixed and a consistent color has been achieved. The heavy whipping cream causes the mixture to thicken the more you mix it. So, I’d recommend using an electric mixer. Once you are satisfied with the color, start mixing in the whipping cream until it has a consistent “chocolate” color thorough. Once your satisfied with the color, spoon the mixture into the pie crust, smooth the top to your liking, and then refrigerate for one hour before serving.
-
 @ 6be5cc06:5259daf0
2025-05-27 20:22:09
@ 6be5cc06:5259daf0
2025-05-27 20:22:09A posição do libertário que rejeita o cristianismo padece de sérias incoerências lógicas, históricas e filosóficas. Ao renegar as bases espirituais e culturais que tornaram possível o próprio ideal libertário, tal posição demonstra ser, ao mesmo tempo, autofágica e irracional. É o caso de alguém que se gloria dos frutos de uma árvore que corta pela raiz.
I. Fundamento histórico: a civilização da liberdade é cristã
Não foi o secularismo moderno, nem o paganismo antigo, que ergueram as instituições que protegem a dignidade da pessoa humana e os limites ao poder. Desde os primeiros séculos, a Igreja resistiu ao culto estatal romano, afirmando a soberania de Deus sobre os Césares — "Mais importa obedecer a Deus que aos homens" (Atos 5,29).
Foi o cristianismo que:
-
Fundou universidades livres, onde o saber era buscado sob o primado da verdade;
-
Defendeu a lei natural como fundamento do direito — uma doutrina que protege o indivíduo contra tiranias;
-
Resgatou e aprofundou o conceito de pessoa, dotada de razão e livre-arbítrio, imagem de Deus, e, portanto, inalienavelmente digna e responsável.
Em momentos-chave da história, como nas disputas entre papado e império, nas resistências contra absolutismos, e na fundação do direito internacional por Francisco de Vitoria e a Escola de Salamanca, foi o cristianismo quem freou o poder estatal em nome de princípios superiores. A tradição cristã foi frequentemente o principal obstáculo à tirania, não seu aliado.
Negar isso é amputar a própria genealogia da liberdade ocidental.
Uma das chaves do cristianismo para a construção dessa civilização da liberdade foi a exaltação do individualismo. Ao afirmar que o ser humano é feito à imagem de Deus e que sua salvação é uma escolha pessoal, o cristianismo colocou o indivíduo no centro da moralidade e da liberdade. Diferente dos gregos, cuja ética era voltada para a polis e a cidade-estado, o cristianismo reafirma a suprema importância do indivíduo, com sua capacidade de escolha moral, responsabilidade pessoal e dignidade intrínseca. Esse princípio, mais do que qualquer outra religião, foi o alicerce do desenvolvimento da liberdade individual e da autonomia, valores que sustentam a civilização ocidental.
A ética grega, na melhor das hipóteses, descreve a ordem natural — mas não consegue justificar por que essa ordem deveria obrigar a vontade humana. Um Logos impessoal não tem autoridade moral. Uma ordem cósmica sem um Legislador é apenas um dado de fato, não uma norma vinculante. A vontade pode rebelar-se contra o telos — e sem um Deus justo, que ordena a natureza à perfeição, não há razão última para não o fazer.
A cultura grega teve uma influência indiscutível sobre o desenvolvimento da civilização ocidental, mas o cristianismo não só absorveu o que havia de bom na cultura grega, como também elevou e completou esses aspectos. O cristianismo, ao afirmar que todos os homens são feitos à imagem e semelhança de Deus e têm dignidade intrínseca, levou a uma noção de igualdade moral e liberdade que transcende as limitações da pólis grega.
II. Falsa dicotomia: fé e liberdade não são opostas
Com frequência equiparam a religião à coerção e à obediência cega. Mas isso é um equívoco: o cristianismo não se impõe pela força, mas apela à consciência. O próprio Deus, em sua relação com a criatura racional, respeita sua liberdade. Como ensina a Escritura:
"Se alguém quiser vir após mim..." (Mt 16,24);
"Eis que estou à porta e bato. Se alguém ouvir a minha voz e abrir a porta, entrarei em sua casa e cearei com ele." (Ap 3,20);
"Assim falai, e assim procedei, como devendo ser julgados pela lei da liberdade." (Tiago 2,12).A adesão à fé deve ser livre, voluntária e racional, pois sem liberdade não há verdadeiro mérito, nem amor genuíno. Isso é mais compatível com o princípio de não agressão do que qualquer utopia secular. Ora, o núcleo do evangelho é voluntarista: salvação pessoal, conversão interior, caridade.
Ninguém deve ser forçado, contra sua vontade, a abraçar a fé, pois o ato de fé é por sua natureza voluntário (Dignitatis Humanae; CDC, cân. 748,2)
Se algum Estado usa da força para impor o cristianismo, afirmar que o cristianismo causou as coerções é tão equivocado quanto dizer que a propriedade privada causa o comunismo; é uma inversão da realidade, pois o comunismo surge precisamente da violação da propriedade. Portanto, a fé forçada é inválida em si mesma, pois viola a natureza do ato de crer, que deve ser livre.
III. Fundamento moral: sem transcendência, o libertarianismo flutua no vácuo
O libertário anticristão busca defender princípios objetivos — como a inviolabilidade do indivíduo e a ilegitimidade da agressão — sem um fundamento transcendente que lhes dê validade universal. Por que a agressão é errada? Por que alguém tem direito à vida, à liberdade, à propriedade? Sem uma explicação transcendental, as respostas para tais perguntas se tornam apenas opiniões ou convenções, não obrigações morais vinculantes. Se a moralidade é puramente humana, então os direitos podem ser modificados ou ignorados conforme a vontade da sociedade. O conceito de direitos naturais, tão caro ao libertarianismo, precisa de um solo metafísico que justifique sua universalidade e imutabilidade. Caso contrário, eles podem ser tratados apenas como acordos utilitários temporários ou preferências culturais, sem qualquer obrigatoriedade para todos os seres humanos em todas as circunstâncias.
Pensadores libertários seculares, como Ayn Rand e Murray Rothbard, tentaram ancorar os direitos naturais na razão humana ou na natureza do homem. Rand baseia sua ética no egoísmo racional, enquanto Rothbard apela à lei natural. Embora essas abordagens busquem objetividade, elas carecem de uma resposta definitiva para por que a razão ou a natureza humana obrigam moralmente todos os indivíduos. Sem um fundamento transcendente, suas concepções permanecem vulneráveis a interpretações subjetivas ou a cálculos utilitários.
Aqui, o cristianismo oferece uma explicação sólida e transcendental que fundamenta os direitos naturais. A visão cristã de que o ser humano foi criado à imagem e semelhança de Deus confere à pessoa uma dignidade intrínseca, imutável e universal. Essa dignidade não depende de fatores externos, como consenso social ou poder político, mas é uma característica inerente ao ser humano pela sua criação divina. A partir dessa perspectiva teológica, torna-se possível afirmar com base sólida que os direitos naturais são dados por Deus e, portanto, são universais e vinculantes.
O cristianismo também é a base de um sistema moral que distingue claramente justiça de legalidade. O Estado pode criar leis, mas isso não significa que essas leis sejam justas. A justiça, sob a ótica cristã, é uma expressão da ordem moral objetiva, algo que transcende as leis humanas e é definido pela vontade divina. Por isso, o libertarianismo cristão vê a agressão como uma violação de uma ordem moral objetiva, e não apenas uma violação de uma convenção social ou de um acordo utilitário.
Se a moralidade e os direitos naturais não forem fundamentados em um Logos criador e legislador, o que acontece é que o conceito de direito natural degenera para algo mais frágil, como um simples acordo utilitário. Nesse cenário, os direitos do indivíduo se tornam algo acordado entre os membros de uma sociedade, em vez de princípios imutáveis e universais. Os direitos podem ser negociados, alterados ou ignorados conforme o interesse do momento.
IV. Fundamento científico: a racionalidade moderna é filha da fé cristã
A ciência moderna só foi possível no contexto cultural cristão. Nenhuma outra civilização — nem a grega, nem a islâmica, nem a chinesa — produziu o método científico como o Ocidente cristão o fez.
Isso se deve a quatro premissas teológicas:
-
Criação racional: O mundo é ordenado por um Deus racional.
-
Distinção entre Criador e criatura: A natureza não é divina e pode ser estudada sem sacrilégio.
-
Valor do trabalho e da observação empírica, herdado do monaquismo.
-
Autonomia institucional, presente nas universidades medievais.
A doutrina cristã da Criação ex nihilo ensina que o mundo foi criado por um Deus racional, sábio e pessoal. Portanto, o cosmos é ordenado, possui leis, e pode ser compreendido pela razão humana — que é imagem do Criador. Isso contrasta fortemente com as cosmovisões panteístas ou mitológicas, onde o mundo é cíclico, arbitrário ou habitado por forças caprichosas.
Sem essa fé no Logos criador, não há razão para crer que a natureza tenha uma ordem inteligível universal e constante, que pode ser descoberta por observação e dedução. A ciência moderna só é possível porque, antes de investigar a natureza, pressupôs-se que ela era investigável — e isso foi uma herança direta do pensamento cristão.
Homens como Bacon, Newton, Kepler e Galileu viam na ciência um modo de glorificar o Criador. O ateísmo cientificista é, portanto, parasitário da teologia cristã, pois toma seus frutos e rejeita suas raízes. A ciência moderna nasceu como filha legítima da fé cristã. E os que hoje a usam contra sua mãe, ou são ingratos, ou ignorantes.
V. O cristianismo como barreira à revolução cultural
O cristianismo é a barreira mais sólida contra a infiltração revolucionária. A chamada "marcha gramsciana", que visa corroer os fundamentos morais da sociedade para subjugar o indivíduo ao coletivo, encontra sua resistência mais firme nos princípios cristãos. A fé cristã, ao proclamar a existência de uma verdade objetiva, de uma lei moral imutável e de uma dignidade humana que transcende o Estado e o consenso social, imuniza a civilização contra o relativismo e o igualitarismo nivelador do marxismo cultural.
Além disso, o cristianismo é uma tradição milenar, profundamente enraizada no cotidiano das pessoas, não sendo uma novidade a ser imposta ou implementada, mas uma força presente há séculos, que permeia a estrutura social, moral e cultural da sociedade. Sua presença constante nas comunidades, desde os tempos mais antigos, oferece uma resistência robusta contra qualquer tentativa de subverter a ordem natural e moral estabelecida.
Não por acaso, tanto Karl Marx quanto Antonio Gramsci identificaram no cristianismo o principal obstáculo à realização de seus projetos revolucionários. Marx chamou a religião de "ópio do povo" porque sabia que uma alma ancorada em Deus não se submete facilmente ao poder terreno; Gramsci, mais sutil, propôs a destruição da cultura cristã como pré-condição para o triunfo do socialismo. Sem essa âncora transcendente, a sociedade torna-se presa fácil das engenharias sociais que pretendem redefinir arbitrariamente o homem, a família e a liberdade.
Conclusão
O libertário anticristão, consciente ou não, nega as fundações mesmas do edifício que habita. Ao rejeitar o cristianismo, cava o abismo sob os próprios pés, privando o ideal libertário de sua base moral, cultural e racional. Ele defende a ética voluntária, a liberdade individual e a ordem espontânea, mas sem o solo metafísico e histórico que torna esses princípios inteligíveis e possíveis. É um erro tentar preservar a liberdade em termos absolutos sem reconhecer as raízes cristãs que a sustentam, pois o cristianismo é a única tradição que a legitima e a viabiliza.
Negar o cristianismo é racionalmente insustentável. A liberdade, como a conhecemos, é filha da fé cristã, que oferece a base moral e metafísica que torna a liberdade tanto desejável quanto possível. Mesmo que ateu, o libertário que ama a liberdade deveria, no mínimo, respeitar — e, idealmente, redescobrir — essas raízes cristãs. Pois sem fé, restam apenas o niilismo e o relativismo, que, eventualmente, desaguam na servidão.
Como nos ensina a tradição: Ubi fides ibi libertas — onde há fé, há liberdade.
-
-
 @ 5391098c:74403a0e
2025-05-27 18:20:42
@ 5391098c:74403a0e
2025-05-27 18:20:42Você trabalha 5 meses do ano somente para pagar impostos. Ou seja, 42% da sua renda serve para bancar serviços públicos de péssima qualidade. Mesmo que você tivesse a liberdade de usar esses 42% da sua renda para contratar serviços privados de qualidade (saúde, segurança e ensino), ainda assim você seria um escravo porque você recebe dinheiro em troca do seu trabalho, e o dinheiro perde cerca de 10% do valor a cada ano. Em outras palavras todo seu dinheiro que sobra depois de comprar comida, vestuário e moradia perde 100% do valor a cada 10 anos. Isso acontece porque o Estado imprime dinheiro do nada e joga na economia de propósito para gerar INFLAÇÃO e manter todos nós escravizados. Você pode deixar seu dinheiro investido em qualquer aplicação que imaginar e ainda assim nunca terá uma rentabilidade superior a inflação real. No final, acaba perdendo tudo do mesmo jeito. Caso você se ache esperto por investir o que sobra da sua renda em bens duráveis como imóveis ou veículos, sabia que esses bens também não são seus, porque se deixar de pagar os impostos desses bens (iptu, itr, ipva) você também perde tudo. Além disso, o custo de manutenção desses bens deve ser levado em consideração na conta das novas dívidas que você assumiu. No caso dos imóveis urbanos é impossível alugá-lo por mais de 0,38% do seu valor mensalmente. Em outras palavras, a cada ano você recebe menos de 5% do que investiu, tem que pagar o custo de manutenção, mais impostos e a valorização do bem nunca será superior a inflação real, também fazendo você perder quase tudo em cerca de 15 anos. A situação é ainda pior com os imóveis rurais e veículos, basta fazer as contas. Caso o dinheiro que você receba em troca do seu trabalho seja suficiente apenas para comprar comida, vestuário e moradia, você já sabe que é um escravo né?… Precisamos entender que a escravidão não acabou, apenas foi democratizada. Hoje a escravidão é financeira, nós somos os castiços e os donos do dinheiro são o senhorio. Os donos do dinheiro são os Globalistas e os Estados seus fantoches. O esquema é simples: fazer todo mundo trabalhar em troca de algo que perde 100% do valor a cada 10 anos, ou seja o dinheiro. Se você pudesse trabalhar em troca de algo que aumentasse de valor acima da inflação real a cada 10 anos você finalmente conquistaria sua liberdade financeira e deixaria de ser escravo. Pois bem, isso já é possível, e não se trata de ouro ou imóveis e sim sobre o Bitcoin, que sobe de valor mais de 100% a cada 10 anos, com a vantagem de ser inconfiscável e de fácil transferência para seus herdeiros quando você morrer, através de uma simples transação LockTime feita em vida. Portanto, mesmo que você não tenha dinheiro para comprar Bitcoin, passar a aceitar Bitcoin em troca de seus produtos e serviços é a única forma de se libertar da escravidão financeira. A carta de alforria financeira proporcionada pelo Bitcoin não é imediata, pois a velocidade da sua libertação depende do quanto você está disposto a aprender sobre o assunto. Eu estou aqui para te ajudar, caso queira. No futuro o Bitcoin estará tão presente na sua vida quanto o pix e o cartão de crédito, você querendo ou não. Assim como o cartão de crédito foi a evolução do cheque pós-datado e o pix a evolução do cartão, o Bitcoin e outras criptomoedas serão a evolução de todos esses meios de pagamento. O que te ofereço é a oportunidade de abolição da sua escravatura antes dos demais escravos acordarem para a realidade, afinal a história sempre se repete: desde o ano de 1300 a.c. a escravidão era defendida pelos próprios escravos, que mais cedo ou mais tarde, foram libertados por Moisés em êxodo 11 da Bíblia Sagrada e hoje o povo de israel se tornou a nação mais rica do mundo. A mesma história se repetiu na Roma Antiga: com o pão e circo. Da mesma forma todo esse império escravocrata ruiu porque mais cedo ou mais tarde os escravos se revoltam, bastam as coisas piorarem bastante. O atual regime de escravidão teve início com a queda do padrão-ouro para impressão do dinheiro no ano de 1944. A escravidão apenas ficou mais sofisticada, pois em vez de pagar os escravos com cerveja como no Egito Antigo ou com pão e circo como na Roma Antiga, passou-se a pagar os escravos com dinheiro sem lastro, ou seja dinheiro inventado, criado do nada, sem qualquer representação com a riqueza real da economia. Mesmo sendo a escravidão atual mais sofisticada, que deixou de ser física para ser financeira, o que torna a mentira mais bem contada, mais cedo ou mais tarde os escravos modernos irão acordar, basta as coisas piorarem mais ou perceberem que todos os bens e serviços do mundo não representam nem 1% de todo o dinheiro que impresso sem lastro. Em outras palavras, se os donos de todo o dinheiro do mundo resolvessem utilizá-lo para comprar tudo o que existe à venda, o preço do quilo do café subiria para R$ 297.306,00 e o preço médio dos imóveis subiria para um número tão grande que sequer caberia nesta folha de papel. Hoje, o dinheiro não vale nada, seus donos sabem disso e optam por entregar o dinheiro aos poucos para os escravos em troca do seu trabalho, para manter o atual regime o máximo de tempo possível. Mesmo assim, o atual regime de escravidão financeira está com os dias contados e depende de você se posicionar antes do efeito manada. Nunca é tarde para entrar no Bitcoin, mesmo ele tendo uma quantidade de emissão limitada, seu valor subirá infinitamente. A menor unidade do Bitcoin é o satoshi, cuja abreviação é sats. Diferente do centavo, cada sat vale um centésimo milionésimo de bitcoin. Hoje (25/05/25), cada unidade de Bitcoin equivale a setecentos mil reais. Logo, cada R$ 0,01 equivale à 0,007 sats. Lembrando que o centavo é um real dividido por cem e o sat é um bitcoin dividido por cem milhões, por isso ainda não existe a paridade entre 1 centavo de real e 1 sat. Essa paridade será alcançada quando um Bitcoin passar a valer um milhão de reais. Com a velocidade que nosso dinheiro está perdendo valor isso não irá demorar muito. Utilizando dados econômicos avançados, prevejo que cada unidade de Bitcoin passará a valer hum milhão de reais até o ano de 2029, assim equiparando 1 sat para cada R$ 0,01. Nesse momento, certamente muitos empresários, comerciantes e profissionais liberais passarão a aceitar o Bitcoin como forma de pagamento pelos seus produtos e serviços, assim como o cheque foi substituído pelo cartão de crédito e o cartão pelo pix. Sabendo disso, você pode entrar na onda de transição no futuro junto com a manada e perder essa alta valorização, ou passar a aceitar Bitcoin agora pelos seus produtos e serviços, assinando assim, a própria carta de alforria da sua escravidão financeira. É importante dizer que os próprios globalistas e governos estão trocando dinheiro por Bitcoin como nunca na história e mesmo que eles adquiram todos os bitcoins disponíveis, ainda assim não será mais possível manter seu regime de escravidão financeira funcionando porque a emissão de Bitcoin é limitada, sendo impossível criar Bitcoin sem lastro, como é feito com o dinheiro hoje. Com o presente artigo, te ofereço a oportunidade de conquistar seus primeiros sats agora, de forma segura e independente, sem precisar de corretoras, bancos, intermediários ou terceiros, basta você querer pois toda a informação necessária está disponível na internet gratuitamente. Se ainda assim você quiser continuar sendo escravo financeiro, depois não adiantar se arrepender quando as janelas de oportunidade se fecharem, o Drex for implantado, papel moeda restringido e sua vida piorar bastante. Importante mencionar que a Lei Brasileira ainda permite a movimentação de até R$ 30.000,00 em Bitcoin por mês sem a necessidade de declaração à Receita Federal e que esse direito pode deixar de existir a qualquer momento, e que quando o Drex for implantado você perderá diversos outros direitos, dentre ele a liberdade de gastar seu dinheiro como quiser e o sigilo. Ofereço ainda, a oportunidade de você baixar uma carteira de Bitcoin gratuita e segura no seu aparelho de celular que funciona de forma semelhante a um banco digital como Nubank e Pagseguro por exemplo, para poder começar à receber Bitcoin pelos seus produtos e serviços agora, de forma fácil e gratuita. Utilizando o qrcode abaixo você ainda ganha alguns sats de graça, promoção válida até o dia 29/05/25 e patrocinada pela Corretora Blink de El Salvador, onde o Bitcoin já é moeda oficial do país, basta acessar o link e instalar o aplicativo: https://get.blink.sv/btcvale
Aviso: disponibilizei o link da carteira de Bitcoin da Corretora Blink apenas como exemplo de como é fácil aceitar Bitcoin como forma de pagamento pelos seus produtos e serviços. Não recomento depender de qualquer corretora para guardar seus valores em Bitcoin. A melhor forma de fazer isso é mantendo dois computadores ou notebook em casa, um conectado à internet com memória em disco disponível de 1 terabyte ou mais para armazenar e visualizar suas transações e outro computador ou notebook desconectado da internet para armazenar suas senhas e chaves privadas para assinar as transações via pendrive. Somente assim você estará 100% livre e seguro. Importante ainda fazer backup em vários CDs com criptografia do seu computador ou notebook que assina as transações, assim também ficando 100% livre e seguro para restaurar sua carteira em qualquer outro computador caso necessário. Todas as instruções de como fazer isso já estão disponíveis gratuitamente na internet. Caso deseje contratar uma consultoria pessoal que inclui aulas particulares por vídeo conferência, onde você aprenderá:
→ Tudo o que precisa saber sobre Bitcoin e demais criptomoedas; → Sistema operacional Linux; → Como instalar sua carteira de Bitcoin em dois computadores para assinaturas air gapped; → Se manter 100% livre e seguro. → Com carga horária à combinar conforme sua disponibilidade.
O custo do investimento pelo meu serviço individual para esse tipo de consultoria é de 204.000 sats (R$ 1.543,46 na cotação atual) valor válido até 31/07/25, interessados entrar em contato por aqui ou através da Matrix: @davipinheiro:matrix.org https://davipinheiro.com/voce-e-escravo-e-nem-sabe-eu-vou-te-provar-agora/
-
 @ 41e6f20b:06049e45
2024-11-17 17:33:55
@ 41e6f20b:06049e45
2024-11-17 17:33:55Let me tell you a beautiful story. Last night, during the speakers' dinner at Monerotopia, the waitress was collecting tiny tips in Mexican pesos. I asked her, "Do you really want to earn tips seriously?" I then showed her how to set up a Cake Wallet, and she started collecting tips in Monero, reaching 0.9 XMR. Of course, she wanted to cash out to fiat immediately, but it solved a real problem for her: making more money. That amount was something she would never have earned in a single workday. We kept talking, and I promised to give her Zoom workshops. What can I say? I love people, and that's why I'm a natural orange-piller.
-
 @ 4ba8e86d:89d32de4
2024-11-14 09:17:14
@ 4ba8e86d:89d32de4
2024-11-14 09:17:14Tutorial feito por nostr:nostr:npub1rc56x0ek0dd303eph523g3chm0wmrs5wdk6vs0ehd0m5fn8t7y4sqra3tk poste original abaixo:
Parte 1 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/263585/tutorial-debloat-de-celulares-android-via-adb-parte-1
Parte 2 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/index.php/263586/tutorial-debloat-de-celulares-android-via-adb-parte-2
Quando o assunto é privacidade em celulares, uma das medidas comumente mencionadas é a remoção de bloatwares do dispositivo, também chamado de debloat. O meio mais eficiente para isso sem dúvidas é a troca de sistema operacional. Custom Rom’s como LineageOS, GrapheneOS, Iodé, CalyxOS, etc, já são bastante enxutos nesse quesito, principalmente quanto não é instalado os G-Apps com o sistema. No entanto, essa prática pode acabar resultando em problemas indesejados como a perca de funções do dispositivo, e até mesmo incompatibilidade com apps bancários, tornando este método mais atrativo para quem possui mais de um dispositivo e separando um apenas para privacidade. Pensando nisso, pessoas que possuem apenas um único dispositivo móvel, que são necessitadas desses apps ou funções, mas, ao mesmo tempo, tem essa visão em prol da privacidade, buscam por um meio-termo entre manter a Stock rom, e não ter seus dados coletados por esses bloatwares. Felizmente, a remoção de bloatwares é possível e pode ser realizada via root, ou mais da maneira que este artigo irá tratar, via adb.
O que são bloatwares?
Bloatware é a junção das palavras bloat (inchar) + software (programa), ou seja, um bloatware é basicamente um programa inútil ou facilmente substituível — colocado em seu dispositivo previamente pela fabricante e operadora — que está no seu dispositivo apenas ocupando espaço de armazenamento, consumindo memória RAM e pior, coletando seus dados e enviando para servidores externos, além de serem mais pontos de vulnerabilidades.
O que é o adb?
O Android Debug Brigde, ou apenas adb, é uma ferramenta que se utiliza das permissões de usuário shell e permite o envio de comandos vindo de um computador para um dispositivo Android exigindo apenas que a depuração USB esteja ativa, mas também pode ser usada diretamente no celular a partir do Android 11, com o uso do Termux e a depuração sem fio (ou depuração wifi). A ferramenta funciona normalmente em dispositivos sem root, e também funciona caso o celular esteja em Recovery Mode.
Requisitos:
Para computadores:
• Depuração USB ativa no celular; • Computador com adb; • Cabo USB;
Para celulares:
• Depuração sem fio (ou depuração wifi) ativa no celular; • Termux; • Android 11 ou superior;
Para ambos:
• Firewall NetGuard instalado e configurado no celular; • Lista de bloatwares para seu dispositivo;
Ativação de depuração:
Para ativar a Depuração USB em seu dispositivo, pesquise como ativar as opções de desenvolvedor de seu dispositivo, e lá ative a depuração. No caso da depuração sem fio, sua ativação irá ser necessária apenas no momento que for conectar o dispositivo ao Termux.
Instalação e configuração do NetGuard
O NetGuard pode ser instalado através da própria Google Play Store, mas de preferência instale pela F-Droid ou Github para evitar telemetria.
F-Droid: https://f-droid.org/packages/eu.faircode.netguard/
Github: https://github.com/M66B/NetGuard/releases
Após instalado, configure da seguinte maneira:
Configurações → padrões (lista branca/negra) → ative as 3 primeiras opções (bloquear wifi, bloquear dados móveis e aplicar regras ‘quando tela estiver ligada’);
Configurações → opções avançadas → ative as duas primeiras (administrar aplicativos do sistema e registrar acesso a internet);
Com isso, todos os apps estarão sendo bloqueados de acessar a internet, seja por wifi ou dados móveis, e na página principal do app basta permitir o acesso a rede para os apps que você vai usar (se necessário). Permita que o app rode em segundo plano sem restrição da otimização de bateria, assim quando o celular ligar, ele já estará ativo.
Lista de bloatwares
Nem todos os bloatwares são genéricos, haverá bloatwares diferentes conforme a marca, modelo, versão do Android, e até mesmo região.
Para obter uma lista de bloatwares de seu dispositivo, caso seu aparelho já possua um tempo de existência, você encontrará listas prontas facilmente apenas pesquisando por elas. Supondo que temos um Samsung Galaxy Note 10 Plus em mãos, basta pesquisar em seu motor de busca por:
Samsung Galaxy Note 10 Plus bloatware listProvavelmente essas listas já terão inclusas todos os bloatwares das mais diversas regiões, lhe poupando o trabalho de buscar por alguma lista mais específica.
Caso seu aparelho seja muito recente, e/ou não encontre uma lista pronta de bloatwares, devo dizer que você acaba de pegar em merda, pois é chato para um caralho pesquisar por cada aplicação para saber sua função, se é essencial para o sistema ou se é facilmente substituível.
De antemão já aviso, que mais para frente, caso vossa gostosura remova um desses aplicativos que era essencial para o sistema sem saber, vai acabar resultando na perda de alguma função importante, ou pior, ao reiniciar o aparelho o sistema pode estar quebrado, lhe obrigando a seguir com uma formatação, e repetir todo o processo novamente.
Download do adb em computadores
Para usar a ferramenta do adb em computadores, basta baixar o pacote chamado SDK platform-tools, disponível através deste link: https://developer.android.com/tools/releases/platform-tools. Por ele, você consegue o download para Windows, Mac e Linux.
Uma vez baixado, basta extrair o arquivo zipado, contendo dentro dele uma pasta chamada platform-tools que basta ser aberta no terminal para se usar o adb.
Download do adb em celulares com Termux.
Para usar a ferramenta do adb diretamente no celular, antes temos que baixar o app Termux, que é um emulador de terminal linux, e já possui o adb em seu repositório. Você encontra o app na Google Play Store, mas novamente recomendo baixar pela F-Droid ou diretamente no Github do projeto.
F-Droid: https://f-droid.org/en/packages/com.termux/
Github: https://github.com/termux/termux-app/releases
Processo de debloat
Antes de iniciarmos, é importante deixar claro que não é para você sair removendo todos os bloatwares de cara sem mais nem menos, afinal alguns deles precisam antes ser substituídos, podem ser essenciais para você para alguma atividade ou função, ou até mesmo são insubstituíveis.
Alguns exemplos de bloatwares que a substituição é necessária antes da remoção, é o Launcher, afinal, é a interface gráfica do sistema, e o teclado, que sem ele só é possível digitar com teclado externo. O Launcher e teclado podem ser substituídos por quaisquer outros, minha recomendação pessoal é por aqueles que respeitam sua privacidade, como Pie Launcher e Simple Laucher, enquanto o teclado pelo OpenBoard e FlorisBoard, todos open-source e disponíveis da F-Droid.
Identifique entre a lista de bloatwares, quais você gosta, precisa ou prefere não substituir, de maneira alguma você é obrigado a remover todos os bloatwares possíveis, modifique seu sistema a seu bel-prazer. O NetGuard lista todos os apps do celular com o nome do pacote, com isso você pode filtrar bem qual deles não remover.
Um exemplo claro de bloatware insubstituível e, portanto, não pode ser removido, é o com.android.mtp, um protocolo onde sua função é auxiliar a comunicação do dispositivo com um computador via USB, mas por algum motivo, tem acesso a rede e se comunica frequentemente com servidores externos. Para esses casos, e melhor solução mesmo é bloquear o acesso a rede desses bloatwares com o NetGuard.
MTP tentando comunicação com servidores externos:
Executando o adb shell
No computador
Faça backup de todos os seus arquivos importantes para algum armazenamento externo, e formate seu celular com o hard reset. Após a formatação, e a ativação da depuração USB, conecte seu aparelho e o pc com o auxílio de um cabo USB. Muito provavelmente seu dispositivo irá apenas começar a carregar, por isso permita a transferência de dados, para que o computador consiga se comunicar normalmente com o celular.
Já no pc, abra a pasta platform-tools dentro do terminal, e execute o seguinte comando:
./adb start-serverO resultado deve ser:
daemon not running; starting now at tcp:5037 daemon started successfully
E caso não apareça nada, execute:
./adb kill-serverE inicie novamente.
Com o adb conectado ao celular, execute:
./adb shellPara poder executar comandos diretamente para o dispositivo. No meu caso, meu celular é um Redmi Note 8 Pro, codinome Begonia.
Logo o resultado deve ser:
begonia:/ $
Caso ocorra algum erro do tipo:
adb: device unauthorized. This adb server’s $ADB_VENDOR_KEYS is not set Try ‘adb kill-server’ if that seems wrong. Otherwise check for a confirmation dialog on your device.
Verifique no celular se apareceu alguma confirmação para autorizar a depuração USB, caso sim, autorize e tente novamente. Caso não apareça nada, execute o kill-server e repita o processo.
No celular
Após realizar o mesmo processo de backup e hard reset citado anteriormente, instale o Termux e, com ele iniciado, execute o comando:
pkg install android-toolsQuando surgir a mensagem “Do you want to continue? [Y/n]”, basta dar enter novamente que já aceita e finaliza a instalação
Agora, vá até as opções de desenvolvedor, e ative a depuração sem fio. Dentro das opções da depuração sem fio, terá uma opção de emparelhamento do dispositivo com um código, que irá informar para você um código em emparelhamento, com um endereço IP e porta, que será usado para a conexão com o Termux.
Para facilitar o processo, recomendo que abra tanto as configurações quanto o Termux ao mesmo tempo, e divida a tela com os dois app’s, como da maneira a seguir:
Para parear o Termux com o dispositivo, não é necessário digitar o ip informado, basta trocar por “localhost”, já a porta e o código de emparelhamento, deve ser digitado exatamente como informado. Execute:
adb pair localhost:porta CódigoDeEmparelhamentoDe acordo com a imagem mostrada anteriormente, o comando ficaria “adb pair localhost:41255 757495”.
Com o dispositivo emparelhado com o Termux, agora basta conectar para conseguir executar os comandos, para isso execute:
adb connect localhost:portaObs: a porta que você deve informar neste comando não é a mesma informada com o código de emparelhamento, e sim a informada na tela principal da depuração sem fio.
Pronto! Termux e adb conectado com sucesso ao dispositivo, agora basta executar normalmente o adb shell:
adb shellRemoção na prática Com o adb shell executado, você está pronto para remover os bloatwares. No meu caso, irei mostrar apenas a remoção de um app (Google Maps), já que o comando é o mesmo para qualquer outro, mudando apenas o nome do pacote.
Dentro do NetGuard, verificando as informações do Google Maps:
Podemos ver que mesmo fora de uso, e com a localização do dispositivo desativado, o app está tentando loucamente se comunicar com servidores externos, e informar sabe-se lá que peste. Mas sem novidades até aqui, o mais importante é que podemos ver que o nome do pacote do Google Maps é com.google.android.apps.maps, e para o remover do celular, basta executar:
pm uninstall –user 0 com.google.android.apps.mapsE pronto, bloatware removido! Agora basta repetir o processo para o resto dos bloatwares, trocando apenas o nome do pacote.
Para acelerar o processo, você pode já criar uma lista do bloco de notas com os comandos, e quando colar no terminal, irá executar um atrás do outro.
Exemplo de lista:
Caso a donzela tenha removido alguma coisa sem querer, também é possível recuperar o pacote com o comando:
cmd package install-existing nome.do.pacotePós-debloat
Após limpar o máximo possível o seu sistema, reinicie o aparelho, caso entre no como recovery e não seja possível dar reboot, significa que você removeu algum app “essencial” para o sistema, e terá que formatar o aparelho e repetir toda a remoção novamente, desta vez removendo poucos bloatwares de uma vez, e reiniciando o aparelho até descobrir qual deles não pode ser removido. Sim, dá trabalho… quem mandou querer privacidade?
Caso o aparelho reinicie normalmente após a remoção, parabéns, agora basta usar seu celular como bem entender! Mantenha o NetGuard sempre executando e os bloatwares que não foram possíveis remover não irão se comunicar com servidores externos, passe a usar apps open source da F-Droid e instale outros apps através da Aurora Store ao invés da Google Play Store.
Referências: Caso você seja um Australopithecus e tenha achado este guia difícil, eis uma videoaula (3:14:40) do Anderson do canal Ciberdef, realizando todo o processo: http://odysee.com/@zai:5/Como-remover-at%C3%A9-200-APLICATIVOS-que-colocam-a-sua-PRIVACIDADE-E-SEGURAN%C3%87A-em-risco.:4?lid=6d50f40314eee7e2f218536d9e5d300290931d23
Pdf’s do Anderson citados na videoaula: créditos ao anon6837264 http://eternalcbrzpicytj4zyguygpmkjlkddxob7tptlr25cdipe5svyqoqd.onion/file/3863a834d29285d397b73a4af6fb1bbe67c888d72d30/t-05e63192d02ffd.pdf
Processo de instalação do Termux e adb no celular: https://youtu.be/APolZrPHSms
-
 @ cff1720e:15c7e2b2
2025-05-28 11:18:23
@ cff1720e:15c7e2b2
2025-05-28 11:18:23Liebe Anwender,\ \ diesmal beginnen die Neuigkeiten schon beim Titel und der Anrede. Unsere Worte bestimmen unser Denken, und daher war die Korrektur wichtiger als sie zunächst erscheint, denn bei Pareto gibt es die klassische Trennung zwischen Autor und Leser nicht mehr. Cocreation heißt unser Konzept, jeder kann publizieren, kommentieren, honorieren und distribuieren. Mag das bei Blogtexten derzeit noch nicht selbstverständlich sein, so ist das bei Bildern längst die Norm.

“Ein Bild sagt mehr als tausend Worte” beschreibt die Wirkung visueller Kommunikation. Deshalb haben wir nach dem Blogtext nun mit Bildern eine neue Content-Kategorie eingeführt. Natürlich auch hier mit den bekannten Funktionen der Interaktion wie like, repost und zap. Es gibt derzeit eine Gliederung in 4 Feeds, Gefolgt (für Nostr-User verfügbar), Memes und Kunst (gefiltert nach entsprechenden Tags) und Pareto für alles andere.
Jeder Nostr-User hat die Möglichkeit eigene Bilder hochzuladen, zu taggen, sowie mit einem Titel und Untertext zu versehen. “Everyone is a creator” war noch nie leichter, probiert es einfach aus! Noch kein Nostr-Profil und trotzdem interessiert? Kein Problem, bitte Informationen zu originellen Bildquellen oder Interesse an Mitwirkung per Mail senden an pictures@pareto.space
Leicht ist es auch die Pareto-Inhalte zu erhalten und konsumieren, man braucht weder einen Account noch spezielle Apps. Jeder hat bereits die entsprechenden Voraussetzungen, hier ein paar Beispiele.\ \ Newsletter per Mail (Die Friedenstaube)\ hier abonnieren\ \ In Telegram lesen -> hier unsere Kanäle\ https://t.me/pareto_artikel \ https://t.me/friedenstaube_artikel \ \ Als Feed in einem Feed-Reader \ https://pareto.space/atom/feed.xml \ https://pareto.space/atom/de_feed.xml \ https://pareto.space/atom/en_feed.xml
Fügt in Eure Artikel bitte am Anfang / Ende einen Hinweis auf den Pareto-Client ein, andere Clients unterstützen nicht alle Features. Das ist ein Service-Hinweis zur besseren Lesbarkeit “Dieser Beitrag wurde mit dem Pareto-Client geschrieben.” Ebenso ist ein Hinweis auf Onboarding bei Nostr nützlich: neue Nostr-User können euch liken und zappen: not yet on Nostr and want the full experience? Easy onboarding via Start.\ \ Das Pareto-Team baut den “Marktplatz der Ideen” und hat dabei schon viel erreicht. Feedback und Mitarbeit hilft uns damit noch schneller voranzukommen, wir bedanken uns für Eure Unterstützung.\ team@pareto.space \ https://pareto.space \ https://geyser.fund/project/pareto?hero=1c1b8e487090
-
 @ eb0157af:77ab6c55
2025-05-28 10:01:29
@ eb0157af:77ab6c55
2025-05-28 10:01:29Michigan lawmakers are unveiling a comprehensive strategy to regulate Bitcoin and cryptocurrencies.
On May 21, Republican Representative Bill Schuette introduced House Bill 4510, a proposal to amend the Michigan Public Employee Retirement System Investment Act. The legislation would allow the state treasurer, currently Rachael Eubanks, to diversify the state’s investments by including cryptocurrencies with an average market capitalization of over $250 million in the past calendar year.
Under current criteria, Bitcoin (BTC) and Ether (ETH) are the only cryptocurrencies that meet these selection standards. The proposal specifies that any investment in digital assets must be made through exchange-traded products (spot ETFs) issued by registered investment companies.
Anti-CBDC legislation
Republican Representative Bryan Posthumus is leading the bipartisan initiative behind the second bill, HB 4511, which establishes protections for cryptocurrency holders. The proposal prohibits Michigan from implementing crypto bans or imposing licensing requirements on digital asset holders.
Another key aspect of the legislation is a ban on state officials from supporting or promoting a potential federal central bank digital currency (CBDC). The definition includes the issuance of memorandums or official statements endorsing CBDC proposals related to testing, adoption, or implementation.
Mining and redevelopment of abandoned sites
The third bill, HB 4512, is a proposal led by Democratic Representative Mike McFall for a bipartisan group. This initiative would establish a Bitcoin mining program allowing operators to use abandoned oil and natural gas sites.
The program calls for the appointment of a supervisor tasked with assessing the site’s remaining productive potential, identifying the last operator, and determining the length of abandonment. Prospective participants would need to submit detailed legal documentation of their organizational structure, demonstrate operational expertise in mining, and provide profitability breakeven estimates for their ventures.
The fourth and final bill, HB 4513, also introduced by the bipartisan group led by McFall, focuses on the fiscal aspect of the HB 4512 initiative. The proposal would amend Michigan’s income tax laws to include proceeds generated from the proposed Bitcoin mining program.
The post Michigan: four bills on pension funds, CBDCs, and mining appeared first on Atlas21.
-
 @ 5391098c:74403a0e
2025-05-27 18:15:38
@ 5391098c:74403a0e
2025-05-27 18:15:38Você trabalha 5 meses do ano somente para pagar impostos. Ou seja, 42% da sua renda serve para bancar serviços públicos de péssima qualidade. Mesmo que você tivesse a liberdade de usar esses 42% da sua renda para contratar serviços privados de qualidade (saúde, segurança e ensino), ainda assim você seria um escravo porque você recebe dinheiro em troca do seu trabalho, e o dinheiro perde cerca de 10% do valor a cada ano. Em outras palavras todo seu dinheiro que sobra depois de comprar comida, vestuário e moradia perde 100% do valor a cada 10 anos. Isso acontece porque o Estado imprime dinheiro do nada e joga na economia de propósito para gerar INFLAÇÃO e manter todos nós escravizados. Você pode deixar seu dinheiro investido em qualquer aplicação que imaginar e ainda assim nunca terá uma rentabilidade superior a inflação real. No final, acaba perdendo tudo do mesmo jeito. Caso você se ache esperto por investir o que sobra da sua renda em bens duráveis como imóveis ou veículos, sabia que esses bens também não são seus, porque se deixar de pagar os impostos desses bens (iptu, itr, ipva) você também perde tudo. Além disso, o custo de manutenção desses bens deve ser levado em consideração na conta das novas dívidas que você assumiu. No caso dos imóveis urbanos é impossível alugá-lo por mais de 0,38% do seu valor mensalmente. Em outras palavras, a cada ano você recebe menos de 5% do que investiu, tem que pagar o custo de manutenção, mais impostos e a valorização do bem nunca será superior a inflação real, também fazendo você perder quase tudo em cerca de 15 anos. A situação é ainda pior com os imóveis rurais e veículos, basta fazer as contas. Caso o dinheiro que você receba em troca do seu trabalho seja suficiente apenas para comprar comida, vestuário e moradia, você já sabe que é um escravo né?… Precisamos entender que a escravidão não acabou, apenas foi democratizada. Hoje a escravidão é financeira, nós somos os castiços e os donos do dinheiro são o senhorio. Os donos do dinheiro são os Globalistas e os Estados seus fantoches. O esquema é simples: fazer todo mundo trabalhar em troca de algo que perde 100% do valor a cada 10 anos, ou seja o dinheiro. Se você pudesse trabalhar em troca de algo que aumentasse de valor acima da inflação real a cada 10 anos você finalmente conquistaria sua liberdade financeira e deixaria de ser escravo. Pois bem, isso já é possível, e não se trata de ouro ou imóveis e sim sobre o Bitcoin, que sobe de valor mais de 100% a cada 10 anos, com a vantagem de ser inconfiscável e de fácil transferência para seus herdeiros quando você morrer, através de uma simples transação LockTime feita em vida. Portanto, mesmo que você não tenha dinheiro para comprar Bitcoin, passar a aceitar Bitcoin em troca de seus produtos e serviços é a única forma de se libertar da escravidão financeira. A carta de alforria financeira proporcionada pelo Bitcoin não é imediata, pois a velocidade da sua libertação depende do quanto você está disposto a aprender sobre o assunto. Eu estou aqui para te ajudar, caso queira. No futuro o Bitcoin estará tão presente na sua vida quanto o pix e o cartão de crédito, você querendo ou não. Assim como o cartão de crédito foi a evolução do cheque pós-datado e o pix a evolução do cartão, o Bitcoin e outras criptomoedas serão a evolução de todos esses meios de pagamento. O que te ofereço é a oportunidade de abolição da sua escravatura antes dos demais escravos acordarem para a realidade, afinal a história sempre se repete: desde o ano de 1300 a.c. a escravidão era defendida pelos próprios escravos, que mais cedo ou mais tarde, foram libertados por Moisés em êxodo 11 da Bíblia Sagrada e hoje o povo de israel se tornou a nação mais rica do mundo. A mesma história se repetiu na Roma Antiga: com o pão e circo. Da mesma forma todo esse império escravocrata ruiu porque mais cedo ou mais tarde os escravos se revoltam, bastam as coisas piorarem bastante. O atual regime de escravidão teve início com a queda do padrão-ouro para impressão do dinheiro no ano de 1944. A escravidão apenas ficou mais sofisticada, pois em vez de pagar os escravos com cerveja como no Egito Antigo ou com pão e circo como na Roma Antiga, passou-se a pagar os escravos com dinheiro sem lastro, ou seja dinheiro inventado, criado do nada, sem qualquer representação com a riqueza real da economia. Mesmo sendo a escravidão atual mais sofisticada, que deixou de ser física para ser financeira, o que torna a mentira mais bem contada, mais cedo ou mais tarde os escravos modernos irão acordar, basta as coisas piorarem mais ou perceberem que todos os bens e serviços do mundo não representam nem 1% de todo o dinheiro que impresso sem lastro. Em outras palavras, se os donos de todo o dinheiro do mundo resolvessem utilizá-lo para comprar tudo o que existe à venda, o preço do quilo do café subiria para R$ 297.306,00 e o preço médio dos imóveis subiria para um número tão grande que sequer caberia nesta folha de papel. Hoje, o dinheiro não vale nada, seus donos sabem disso e optam por entregar o dinheiro aos poucos para os escravos em troca do seu trabalho, para manter o atual regime o máximo de tempo possível. Mesmo assim, o atual regime de escravidão financeira está com os dias contados e depende de você se posicionar antes do efeito manada. Nunca é tarde para entrar no Bitcoin, mesmo ele tendo uma quantidade de emissão limitada, seu valor subirá infinitamente. A menor unidade do Bitcoin é o satoshi, cuja abreviação é sats. Diferente do centavo, cada sat vale um centésimo milionésimo de bitcoin. Hoje (25/05/25), cada unidade de Bitcoin equivale a setecentos mil reais. Logo, cada R$ 0,01 equivale à 0,007 sats. Lembrando que o centavo é um real dividido por cem e o sat é um bitcoin dividido por cem milhões, por isso ainda não existe a paridade entre 1 centavo de real e 1 sat. Essa paridade será alcançada quando um Bitcoin passar a valer um milhão de reais. Com a velocidade que nosso dinheiro está perdendo valor isso não irá demorar muito. Utilizando dados econômicos avançados, prevejo que cada unidade de Bitcoin passará a valer hum milhão de reais até o ano de 2029, assim equiparando 1 sat para cada R$ 0,01. Nesse momento, certamente muitos empresários, comerciantes e profissionais liberais passarão a aceitar o Bitcoin como forma de pagamento pelos seus produtos e serviços, assim como o cheque foi substituído pelo cartão de crédito e o cartão pelo pix. Sabendo disso, você pode entrar na onda de transição no futuro junto com a manada e perder essa alta valorização, ou passar a aceitar Bitcoin agora pelos seus produtos e serviços, assinando assim, a própria carta de alforria da sua escravidão financeira. É importante dizer que os próprios globalistas e governos estão trocando dinheiro por Bitcoin como nunca na história e mesmo que eles adquiram todos os bitcoins disponíveis, ainda assim não será mais possível manter seu regime de escravidão financeira funcionando porque a emissão de Bitcoin é limitada, sendo impossível criar Bitcoin sem lastro, como é feito com o dinheiro hoje. Com o presente artigo, te ofereço a oportunidade de conquistar seus primeiros sats agora, de forma segura e independente, sem precisar de corretoras, bancos, intermediários ou terceiros, basta você querer pois toda a informação necessária está disponível na internet gratuitamente. Se ainda assim você quiser continuar sendo escravo financeiro, depois não adiantar se arrepender quando as janelas de oportunidade se fecharem, o Drex for implantado, papel moeda restringido e sua vida piorar bastante. Importante mencionar que a Lei Brasileira ainda permite a movimentação de até R$ 30.000,00 em Bitcoin por mês sem a necessidade de declaração à Receita Federal e que esse direito pode deixar de existir a qualquer momento, e que quando o Drex for implantado você perderá diversos outros direitos, dentre ele a liberdade de gastar seu dinheiro como quiser e o sigilo. Ofereço ainda, a oportunidade de você baixar uma carteira de Bitcoin gratuita e segura no seu aparelho de celular que funciona de forma semelhante a um banco digital como Nubank e Pagseguro por exemplo, para poder começar à receber Bitcoin pelos seus produtos e serviços agora, de forma fácil e gratuita. Utilizando o qrcode abaixo você ainda ganha alguns sats de graça, promoção válida até o dia 29/05/25 e patrocinada pela Corretora Blink de El Salvador, onde o Bitcoin já é moeda oficial do país, basta acessar o link e instalar o aplicativo: https://get.blink.sv/btcvale
Aviso: disponibilizei o link da carteira de Bitcoin da Corretora Blink apenas como exemplo de como é fácil aceitar Bitcoin como forma de pagamento pelos seus produtos e serviços. Não recomento depender de qualquer corretora para guardar seus valores em Bitcoin. A melhor forma de fazer isso é mantendo dois computadores ou notebook em casa, um conectado à internet com memória em disco disponível de 1 terabyte ou mais para armazenar e visualizar suas transações e outro computador ou notebook desconectado da internet para armazenar suas senhas e chaves privadas para assinar as transações via pendrive. Somente assim você estará 100% livre e seguro. Importante ainda fazer backup em vários CDs com criptografia do seu computador ou notebook que assina as transações, assim também ficando 100% livre e seguro para restaurar sua carteira em qualquer outro computador caso necessário. Todas as instruções de como fazer isso já estão disponíveis gratuitamente na internet. Caso deseje contratar uma consultoria pessoal que inclui aulas particulares por vídeo conferência, onde você aprenderá:
→ Tudo o que precisa saber sobre Bitcoin e demais criptomoedas; → Sistema operacional Linux; → Como instalar sua carteira de Bitcoin em dois computadores para assinaturas air gapped; → Se manter 100% livre e seguro. → Com carga horária à combinar conforme sua disponibilidade.
O custo do investimento pelo meu serviço individual para esse tipo de consultoria é de 204.000 sats (R$ 1.543,46 na cotação atual) valor válido até 31/07/25, interessados entrar em contato por aqui ou através da Matrix: @davipinheiro:matrix.org https://davipinheiro.com/voce-e-escravo-e-nem-sabe-eu-vou-te-provar-agora/
-
 @ f0fcbea6:7e059469
2025-05-27 18:08:04
@ f0fcbea6:7e059469
2025-05-27 18:08:04Muita gente, hoje em dia, acha que a leitura já não é tão necessária quanto foi no passado. O rádio e a televisão acabaram assumindo as funções que outrora pertenciam à mídia impressa, da mesma maneira que a fotografia assumiu as funções que outrora pertenciam à pintura e às artes gráficas. Temos de reconhecer - é verdade - que a televisão cumpre algumas dessas funções muito bem; a comunicação visual dos telejornais, por exemplo, tem impacto enorme. A capacidade do rádio em transmitir informações enquanto estamos ocupados - dirigindo um carro, por exemplo - é algo extraordinário, além de nos poupar muito tempo. No entanto, é necessário questionar se as comunicações modernas realmente aumentam o conhecimento sobre o mundo à nossa volta.
Talvez hoje saibamos mais sobre o mundo do que no passado. Dado que o conhecimento é pré-requisito para o entendimento, trata-se de algo bom. Mas o conhecimento não é um pré-requisito tão importante ao entendimento quanto normalmente se supõe. Não precisamos saber tudo sobre determinada coisa para que possamos entendê-la. Uma montanha de fatos pode provocar o efeito contrário, isto é, pode servir de obstáculo ao entendimento. Há uma sensação, hoje em dia, de que temos acesso a muitos fatos, mas não necessariamente ao entendimento desses fatos.
Uma das causas dessa situação é que a própria mídia é projetada para tornar o pensamento algo desnecessário - embora, é claro, isso seja apenas mera impressão. O ato de empacotar ideias e opiniões intelectuais é uma atividade à qual algumas das mentes mais brilhantes se dedicam com grande diligência. O telespectador, o ouvinte, o leitor de revistas - todos eles se defrontam com um amálgama de elementos complexos, desde discursos retóricos minuciosamente planejados até dados estatísticos cuidadosamente selecionados, cujo objetivo é facilitar o ato de "formar a opinião" das pessoas com esforço e dificuldade mínimos. Por vezes, no entanto, o empacotamento é feito de maneira tão eficiente, tão condensada, que o telespectador, o ouvinte ou o leitor não conseguem formar sua opinião. Em vez disso, a opinião empacotada é introjetada em sua mente mais ou menos como uma gravação é inserida no aparelho de som. No momento apropriado, aperta-se o play e a opinião é "tocada". Eles reproduzem a opinião sem terem pensado a respeito.
-
 @ 3bf0c63f:aefa459d
2024-03-19 14:01:01
@ 3bf0c63f:aefa459d
2024-03-19 14:01:01Nostr is not decentralized nor censorship-resistant
Peter Todd has been saying this for a long time and all the time I've been thinking he is misunderstanding everything, but I guess a more charitable interpretation is that he is right.
Nostr today is indeed centralized.
Yesterday I published two harmless notes with the exact same content at the same time. In two minutes the notes had a noticeable difference in responses:
The top one was published to
wss://nostr.wine,wss://nos.lol,wss://pyramid.fiatjaf.com. The second was published to the relay where I generally publish all my notes to,wss://pyramid.fiatjaf.com, and that is announced on my NIP-05 file and on my NIP-65 relay list.A few minutes later I published that screenshot again in two identical notes to the same sets of relays, asking if people understood the implications. The difference in quantity of responses can still be seen today:
These results are skewed now by the fact that the two notes got rebroadcasted to multiple relays after some time, but the fundamental point remains.
What happened was that a huge lot more of people saw the first note compared to the second, and if Nostr was really censorship-resistant that shouldn't have happened at all.
Some people implied in the comments, with an air of obviousness, that publishing the note to "more relays" should have predictably resulted in more replies, which, again, shouldn't be the case if Nostr is really censorship-resistant.
What happens is that most people who engaged with the note are following me, in the sense that they have instructed their clients to fetch my notes on their behalf and present them in the UI, and clients are failing to do that despite me making it clear in multiple ways that my notes are to be found on
wss://pyramid.fiatjaf.com.If we were talking not about me, but about some public figure that was being censored by the State and got banned (or shadowbanned) by the 3 biggest public relays, the sad reality would be that the person would immediately get his reach reduced to ~10% of what they had before. This is not at all unlike what happened to dozens of personalities that were banned from the corporate social media platforms and then moved to other platforms -- how many of their original followers switched to these other platforms? Probably some small percentage close to 10%. In that sense Nostr today is similar to what we had before.
Peter Todd is right that if the way Nostr works is that you just subscribe to a small set of relays and expect to get everything from them then it tends to get very centralized very fast, and this is the reality today.
Peter Todd is wrong that Nostr is inherently centralized or that it needs a protocol change to become what it has always purported to be. He is in fact wrong today, because what is written above is not valid for all clients of today, and if we drive in the right direction we can successfully make Peter Todd be more and more wrong as time passes, instead of the contrary.
See also:
-
 @ c1e9ab3a:9cb56b43
2025-05-27 16:19:06
@ c1e9ab3a:9cb56b43
2025-05-27 16:19:06Star Wars is often viewed as a myth of rebellion, freedom, and resistance to tyranny. The iconography—scrappy rebels, totalitarian stormtroopers, lone smugglers—suggests a deep anti-authoritarian ethos. Yet, beneath the surface, the narrative arc of Star Wars consistently affirms the necessity, even sanctity, of central authority. This blog entry introduces the question: Is Star Wars fundamentally a celebration of statism?
Rebellion as Restoration, Not Revolution
The Rebel Alliance’s mission is not to dismantle centralized power, but to restore the Galactic Republic—a bureaucratic, centrally governed institution. Characters like Mon Mothma and Bail Organa are high-ranking senators, not populist revolutionaries. The goal is to remove the corrupt Empire and reinstall a previous central authority, presumed to be just.
- Rebels are loyalists to a prior state structure.
- Power is not questioned, only who wields it.
Jedi as Centralized Moral Elites
The Jedi, often idealized as protectors of peace, are unelected, extra-legal enforcers of moral and military order. Their authority stems from esoteric metaphysical abilities rather than democratic legitimacy.
- They answer only to their internal Council.
- They are deployed by the Senate, but act independently of civil law.
- Their collapse is depicted as tragic not because they were unaccountable, but because they were betrayed.
This positions them as a theocratic elite, not spiritual anarchists.
Chaos and the Frontier: The Case of the Cantina
The Mos Eisley cantina, often viewed as a symbol of frontier freedom, reveals something darker. It is: - Lawless - Violent - Culturally fragmented
Conflict resolution occurs through murder, not mediation. Obi-Wan slices off a limb; Han shoots first—both without legal consequence. There is no evidence of property rights, dispute resolution, or voluntary order.
This is not libertarian pluralism—it’s moral entropy. The message: without centralized governance, barbarism reigns.
The Mythic Arc: Restoration of the Just State
Every trilogy in the saga returns to a single theme: the fall and redemption of legitimate authority.
- Prequels: Republic collapses into tyranny.
- Originals: Rebels fight to restore legitimate order.
- Sequels: Weak governance leads to resurgence of authoritarianism; heroes must reestablish moral centralism.
The story is not anti-state—it’s anti-bad state. The solution is never decentralization; it’s the return of the right ruler or order.
Conclusion: The Hidden Statism of a Rebel Myth
Star Wars wears the costume of rebellion, but tells the story of centralized salvation. It: - Validates elite moral authority (Jedi) - Romanticizes restoration of fallen governments (Republic) - Portrays decentralized zones as corrupt and savage (outer rim worlds)
It is not an anarchist parable, nor a libertarian fable. It is a statist mythology, clothed in the spectacle of rebellion. Its core message is not that power should be abolished, but that power belongs to the virtuous few.
Question to Consider:
If the Star Wars universe consistently affirms the need for centralized moral and political authority, should we continue to see it as a myth of freedom? Or is it time to recognize it as a narrative of benevolent empire? -
 @ 33baa074:3bb3a297
2025-05-28 08:54:40
@ 33baa074:3bb3a297
2025-05-28 08:54:40COD (chemical oxygen demand) sensors play a vital role in water quality testing. Their main functions include real-time monitoring, pollution event warning, water quality assessment and pollution source tracking. The following are the specific roles and applications of COD sensors in water quality testing:
Real-time monitoring and data acquisition COD sensors can monitor the COD content in water bodies in real time and continuously. Compared with traditional sampling methods, COD sensors are fast and accurate, without manual sampling and laboratory testing, which greatly saves time and labor costs. By combining with the data acquisition system, the monitoring data can be uploaded to the cloud in real time to form a extemporization distribution map of the COD content in the water body, providing detailed data support for environmental monitoring and management.
Pollution event warning and rapid response COD sensors play an important role in early warning and rapid response in water environment monitoring. Once there is an abnormal increase in organic matter in the water body, the COD sensor can quickly detect the change in COD content and alarm through the preset threshold. This enables relevant departments to take measures at the early stage of the pollution incident to prevent the spread of pollution and protect the water environment.
Water quality assessment and pollution source tracking COD sensors play an important role in water quality assessment and pollution source tracking. By continuously monitoring the COD content in water bodies, the water quality can be evaluated and compared with national and regional water quality standards. At the same time, COD sensors can also help determine and track the location and spread of pollution sources, provide accurate data support for environmental management departments, and guide the development of pollution prevention and control work.
Application scenarios COD sensors are widely used in various water quality monitoring scenarios, including but not limited to: Sewage treatment plants: used to monitor the COD content of in fluent and effluent to ensure the effect of sewage treatment. Water source protection and management: deployed in water sources to monitor the COD content of in fluent sources. Once the water quality exceeds the set limit, the system will issue an alarm in time to ensure water quality safety. Lake and river monitoring: deployed in water bodies such as lakes and rivers to monitor the COD content of water bodies in real time.

Technical features of COD sensor COD sensor uses advanced technology, such as ultraviolet absorption method, which does not require the use of chemical reagents, avoiding the risk of contamination of chemical reagents in traditional COD detection methods, and can achieve online uninterrupted water quality monitoring, providing strong support for real-time water quality assessment. In addition, COD sensor also has the advantages of low cost, high stability, strong anti-interference ability, and convenient installation.
Summary In summary, COD sensor plays an irreplaceable role in water quality detection. It can not only provide real-time and accurate water quality data, but also quickly warn when pollution incidents occur, providing strong technical support for water quality management and environmental protection. With the advancement of technology and the popularization of applications, COD sensor will play a more important role in water quality monitoring in the future.
-
 @ d360efec:14907b5f
2025-05-27 15:46:26
@ d360efec:14907b5f
2025-05-27 15:46:26 -
 @ bf47c19e:c3d2573b
2025-05-27 14:57:56
@ bf47c19e:c3d2573b
2025-05-27 14:57:56Srpski prevod knjige "The Little Bitcoin Book"
Zašto je Bitkoin bitan za vašu slobodu, finansije i budućnost?
Verovatno ste čuli za Bitkoin u vestima ili da o njemu raspravljaju vaši prijatelji ili kolege. Kako to da se cena stalno menja? Da li je Bitkoin dobra investicija? Kako to uopšte ima vrednost? Zašto ljudi stalno govore o tome kao da će promeniti svet?
"Mala knjiga o Bitkoinu" govori o tome šta nije u redu sa današnjim novcem i zašto je Bitkoin izmišljen da obezbedi alternativu trenutnom sistemu. Jednostavnim rečima opisuje šta je Bitkoin, kako funkcioniše, zašto je vredan i kako utiče na individualnu slobodu i mogućnosti ljudi svuda - od Nigerije preko Filipina do Venecuele do Sjedinjenih Država. Ova knjiga takođe uključuje odeljak "Pitanja i odgovori" sa nekim od najčešće postavljanih pitanja o Bitkoinu.
Ako želite da saznate više o ovom novom obliku novca koji i dalje izaziva interesovanje i usvajanje širom sveta, onda je ova knjiga za vas.
-
 @ e6ce6154:275e3444
2023-07-27 14:12:49
@ e6ce6154:275e3444
2023-07-27 14:12:49Este artigo foi censurado pelo estado e fomos obrigados a deletá-lo após ameaça de homens armados virem nos visitar e agredir nossa vida e propriedade.
Isto é mais uma prova que os autoproclamados antirracistas são piores que os racistas.
https://rothbardbrasil.com/pelo-direito-de-ser-racista-fascista-machista-e-homofobico
Segue artigo na íntegra. 👇
Sem dúvida, a escalada autoritária do totalitarismo cultural progressista nos últimos anos tem sido sumariamente deletéria e prejudicial para a liberdade de expressão. Como seria de se esperar, a cada dia que passa o autoritarismo progressista continua a se expandir de maneira irrefreável, prejudicando a liberdade dos indivíduos de formas cada vez mais deploráveis e contundentes.
Com a ascensão da tirania politicamente correta e sua invasão a todos os terrenos culturais, o autoritarismo progressista foi se alastrando e consolidando sua hegemonia em determinados segmentos. Com a eventual eclosão e a expansão da opressiva e despótica cultura do cancelamento — uma progênie inevitável do totalitarismo progressista —, todas as pessoas que manifestam opiniões, crenças ou posicionamentos que não estão alinhados com as pautas universitárias da moda tornam-se um alvo.
Há algumas semanas, vimos a enorme repercussão causada pelo caso envolvendo o jogador profissional de vôlei Maurício Sousa, que foi cancelado pelo simples fato de ter emitido sua opinião pessoal sobre um personagem de história em quadrinhos, Jon Kent, o novo Superman, que é bissexual. Maurício Sousa reprovou a conduta sexual do personagem, o que é um direito pessoal inalienável que ele tem. Ele não é obrigado a gostar ou aprovar a bissexualidade. Como qualquer pessoa, ele tem o direito pleno de criticar tudo aquilo que ele não gosta. No entanto, pelo simples fato de emitir a sua opinião pessoal, Maurício Sousa foi acusado de homofobia e teve seu contrato rescindido, sendo desligado do Minas Tênis Clube.
Lamentavelmente, Maurício Sousa não foi o primeiro e nem será o último indivíduo a sofrer com a opressiva e autoritária cultura do cancelamento. Como uma tirania cultural que está em plena ascensão e usufrui de um amplo apoio do establishment, essa nova forma de totalitarismo cultural colorido e festivo está se impondo de formas e maneiras bastante contundentes em praticamente todas as esferas da sociedade contemporânea. Sua intenção é relegar ao ostracismo todos aqueles que não se curvam ao totalitarismo progressista, criminalizando opiniões e crenças que divergem do culto à libertinagem hedonista pós-moderna. Oculto por trás de todo esse ativismo autoritário, o que temos de fato é uma profunda hostilidade por padrões morais tradicionalistas, cristãos e conservadores.
No entanto, é fundamental entendermos uma questão imperativa, que explica em partes o conflito aqui criado — todos os progressistas contemporâneos são crias oriundas do direito positivo. Por essa razão, eles jamais entenderão de forma pragmática e objetiva conceitos como criminalidade, direitos de propriedade, agressão e liberdade de expressão pela perspectiva do jusnaturalismo, que é manifestamente o direito em seu estado mais puro, correto, ético e equilibrado.
Pela ótica jusnaturalista, uma opinião é uma opinião. Ponto final. E absolutamente ninguém deve ser preso, cancelado, sabotado ou boicotado por expressar uma opinião particular sobre qualquer assunto. Palavras não agridem ninguém, portanto jamais poderiam ser consideradas um crime em si. Apenas deveriam ser tipificados como crimes agressões de caráter objetivo, como roubo, sequestro, fraude, extorsão, estupro e infrações similares, que representam uma ameaça direta à integridade física da vítima, ou que busquem subtrair alguma posse empregando a violência.
Infelizmente, a geração floquinho de neve — terrivelmente histérica, egocêntrica e sensível — fica profundamente ofendida e consternada sempre que alguém defende posicionamentos contrários à religião progressista. Por essa razão, os guerreiros da justiça social sinceramente acreditam que o papai-estado deve censurar todas as opiniões que eles não gostam de ouvir, assim como deve também criar leis para encarcerar todos aqueles que falam ou escrevem coisas que desagradam a militância.
Como a geração floquinho de neve foi criada para acreditar que todas as suas vontades pessoais e disposições ideológicas devem ser sumariamente atendidas pelo papai-estado, eles embarcaram em uma cruzada moral que pretende erradicar todas as coisas que são ofensivas à ideologia progressista; só assim eles poderão deflagrar na Terra o seu tão sonhado paraíso hedonista e igualitário, de inimaginável esplendor e felicidade.
Em virtude do seu comportamento intrinsecamente despótico, autoritário e egocêntrico, acaba sendo inevitável que militantes progressistas problematizem tudo aquilo que os desagrada.
Como são criaturas inúteis destituídas de ocupação real e verdadeiro sentido na vida, sendo oprimidas unicamente na sua própria imaginação, militantes progressistas precisam constantemente inventar novos vilões para serem combatidos.
Partindo dessa perspectiva, é natural para a militância que absolutamente tudo que exista no mundo e que não se enquadra com as regras autoritárias e restritivas da religião progressista seja encarado como um problema. Para a geração floquinho de neve, o capitalismo é um problema. O fascismo é um problema. A iniciativa privada é um problema. O homem branco, tradicionalista, conservador e heterossexual é um problema. A desigualdade é um problema. A liberdade é um problema. Monteiro Lobato é um problema (sim, até mesmo o renomado ícone da literatura brasileira, autor — entre outros títulos — de Urupês, foi vítima da cultura do cancelamento, acusado de ser racista e eugenista).
Para a esquerda, praticamente tudo é um problema. Na mentalidade da militância progressista, tudo é motivo para reclamação. Foi em função desse comportamento histérico, histriônico e infantil que o famoso pensador conservador-libertário americano P. J. O’Rourke afirmou que “o esquerdismo é uma filosofia de pirralhos chorões”. O que é uma verdade absoluta e irrefutável em todos os sentidos.
De fato, todas as filosofias de esquerda de forma geral são idealizações utópicas e infantis de um mundo perfeito. Enquanto o mundo não se transformar naquela colorida e vibrante utopia que é apresentada pela cartilha socialista padrão, militantes continuarão a reclamar contra tudo o que existe no mundo de forma agressiva, visceral e beligerante. Evidentemente, eles não vão fazer absolutamente nada de positivo ou construtivo para que o mundo se transforme no gracioso paraíso que eles tanto desejam ver consolidado, mas eles continuarão a berrar e vociferar muito em sua busca incessante pela utopia, marcando presença em passeatas inúteis ou combatendo o fascismo imaginário nas redes sociais.
Sem dúvida, estamos muito perto de ver leis absurdas e estúpidas sendo implementadas, para agradar a militância da terra colorida do assistencialismo eterno onde nada é escasso e tudo cai do céu. Em breve, você não poderá usar calças pretas, pois elas serão consideradas peças de vestuário excessivamente heterossexuais. Apenas calças amarelas ou coloridas serão permitidas. Você também terá que tingir de cor-de-rosa uma mecha do seu cabelo; pois preservar o seu cabelo na sua cor natural é heteronormativo demais da sua parte, sendo portanto um componente demasiadamente opressor da sociedade.
Você também não poderá ver filmes de guerra ou de ação, apenas comédias românticas, pois certos gêneros de filmes exaltam a violência do patriarcado e isso impede o mundo de se tornar uma graciosa festa colorida de fraternidades universitárias ungidas por pôneis resplandecentes, hedonismo infinito, vadiagem universitária e autogratificação psicodélica, que certamente são elementos indispensáveis para se produzir o paraíso na Terra.
Sabemos perfeitamente, no entanto, que dentre as atitudes “opressivas” que a militância progressista mais se empenha em combater, estão o racismo, o fascismo, o machismo e a homofobia. No entanto, é fundamental entender que ser racista, fascista, machista ou homofóbico não são crimes em si. Na prática, todos esses elementos são apenas traços de personalidade; e eles não podem ser pura e simplesmente criminalizados porque ideólogos e militantes progressistas iluminados não gostam deles.
Tanto pela ética quanto pela ótica jusnaturalista, é facilmente compreensível entender que esses traços de personalidade não podem ser criminalizados ou proibidos simplesmente porque integrantes de uma ideologia não tem nenhuma apreciação ou simpatia por eles. Da mesma forma, nenhum desses traços de personalidade representa em si um perigo para a sociedade, pelo simples fato de existir. Por incrível que pareça, até mesmo o machismo, o racismo, o fascismo e a homofobia merecem a devida apologia.
Mas vamos analisar cada um desses tópicos separadamente para entender isso melhor.
Racismo
Quando falamos no Japão, normalmente não fazemos nenhuma associação da sociedade japonesa com o racismo. No entanto, é incontestável o fato de que a sociedade japonesa pode ser considerada uma das sociedades mais racistas do mundo. E a verdade é que não há absolutamente nada de errado com isso.
Aproximadamente 97% da população do Japão é nativa; apenas 3% do componente populacional é constituído por estrangeiros (a população do Japão é estimada em aproximadamente 126 milhões de habitantes). Isso faz a sociedade japonesa ser uma das mais homogêneas do mundo. As autoridades japonesas reconhecidamente dificultam processos de seleção e aplicação a estrangeiros que desejam se tornar residentes. E a maioria dos japoneses aprova essa decisão.
Diversos estabelecimentos comerciais como hotéis, bares e restaurantes por todo o país tem placas na entrada que dizem “somente para japoneses” e a maioria destes estabelecimentos se recusa ostensivamente a atender ou aceitar clientes estrangeiros, não importa quão ricos ou abastados sejam.
Na Terra do Sol Nascente, a hostilidade e a desconfiança natural para com estrangeiros é tão grande que até mesmo indivíduos que nascem em algum outro país, mas são filhos de pais japoneses, não são considerados cidadãos plenamente japoneses.
Se estes indivíduos decidem sair do seu país de origem para se estabelecer no Japão — mesmo tendo descendência nipônica legítima e inquestionável —, eles enfrentarão uma discriminação social considerável, especialmente se não dominarem o idioma japonês de forma impecável. Esse fato mostra que a discriminação é uma parte tão indissociável quanto elementar da sociedade japonesa, e ela está tão profundamente arraigada à cultura nipônica que é praticamente impossível alterá-la ou atenuá-la por qualquer motivo.
A verdade é que — quando falamos de um país como o Japão — nem todos os discursos politicamente corretos do mundo, nem a histeria progressista ocidental mais inflamada poderão algum dia modificar, extirpar ou sequer atenuar o componente racista da cultura nipônica. E isso é consequência de uma questão tão simples quanto primordial: discriminar faz parte da natureza humana, sendo tanto um direito individual quanto um elemento cultural inerente à muitas nações do mundo. Os japoneses não tem problema algum em admitir ou institucionalizar o seu preconceito, justamente pelo fato de que a ideologia politicamente correta não tem no oriente a força e a presença que tem no ocidente.
E é fundamental enfatizar que, sendo de natureza pacífica — ou seja, não violando nem agredindo terceiros —, a discriminação é um recurso natural dos seres humanos, que está diretamente associada a questões como familiaridade e segurança.
Absolutamente ninguém deve ser forçado a apreciar ou integrar-se a raças, etnias, pessoas ou tribos que não lhe transmitem sentimentos de segurança ou familiaridade. Integração forçada é o verdadeiro crime, e isso diversos países europeus — principalmente os escandinavos (países que lideram o ranking de submissão à ideologia politicamente correta) — aprenderam da pior forma possível.
A integração forçada com imigrantes islâmicos resultou em ondas de assassinato, estupro e violência inimagináveis para diversos países europeus, até então civilizados, que a imprensa ocidental politicamente correta e a militância progressista estão permanentemente tentando esconder, porque não desejam que o ocidente descubra como a agenda “humanitária” de integração forçada dos povos muçulmanos em países do Velho Mundo resultou em algumas das piores chacinas e tragédias na história recente da Europa.
Ou seja, ao discriminarem estrangeiros, os japoneses estão apenas se protegendo e lutando para preservar sua nação como um ambiente cultural, étnico e social que lhe é seguro e familiar, assim se opondo a mudanças bruscas, indesejadas e antinaturais, que poderiam comprometer a estabilidade social do país.
A discriminação — sendo de natureza pacífica —, é benévola, salutar e indubitavelmente ajuda a manter a estabilidade social da comunidade. Toda e qualquer forma de integração forçada deve ser repudiada com veemência, pois, mais cedo ou mais tarde, ela irá subverter a ordem social vigente, e sempre será acompanhada de deploráveis e dramáticos resultados.
Para citar novamente os países escandinavos, a Suécia é um excelente exemplo do que não fazer. Tendo seguido o caminho contrário ao da discriminação racional praticada pela sociedade japonesa, atualmente a sociedade sueca — além de afundar de forma consistente na lama da libertinagem, da decadência e da deterioração progressista — sofre em demasia com os imigrantes muçulmanos, que foram deixados praticamente livres para matar, saquear, esquartejar e estuprar quem eles quiserem. Hoje, eles são praticamente intocáveis, visto que denunciá-los, desmoralizá-los ou acusá-los de qualquer crime é uma atitude politicamente incorreta e altamente reprovada pelo establishment progressista. A elite socialista sueca jamais se atreve a acusá-los de qualquer crime, pois temem ser classificados como xenófobos e intolerantes. Ou seja, a desgraça da Europa, sobretudo dos países escandinavos, foi não ter oferecido nenhuma resistência à ideologia progressista politicamente correta. Hoje, eles são totalmente submissos a ela.
O exemplo do Japão mostra, portanto — para além de qualquer dúvida —, a importância ética e prática da discriminação, que é perfeitamente aceitável e natural, sendo uma tendência inerente aos seres humanos, e portanto intrínseca a determinados comportamentos, sociedades e culturas.
Indo ainda mais longe nessa questão, devemos entender que na verdade todos nós discriminamos, e não existe absolutamente nada de errado nisso. Discriminar pessoas faz parte da natureza humana e quem se recusa a admitir esse fato é um hipócrita. Mulheres discriminam homens na hora de selecionar um parceiro; elas avaliam diversos quesitos, como altura, aparência, status social, condição financeira e carisma. E dentre suas opções, elas sempre escolherão o homem mais atraente, másculo e viril, em detrimento de todos os baixinhos, calvos, carentes, frágeis e inibidos que possam estar disponíveis. Da mesma forma, homens sempre terão preferência por mulheres jovens, atraentes e delicadas, em detrimento de todas as feministas de meia-idade, acima do peso, de cabelo pintado, que são mães solteiras e militantes socialistas. A própria militância progressista discrimina pessoas de forma virulenta e intransigente, como fica evidente no tratamento que dispensam a mulheres bolsonaristas e a negros de direita.
A verdade é que — não importa o nível de histeria da militância progressista — a discriminação é inerente à condição humana e um direito natural inalienável de todos. É parte indissociável da natureza humana e qualquer pessoa pode e deve exercer esse direito sempre que desejar. Não existe absolutamente nada de errado em discriminar pessoas. O problema real é a ideologia progressista e o autoritarismo politicamente correto, movimentos tirânicos que não respeitam o direito das pessoas de discriminar.
Fascismo
Quando falamos de fascismo, precisamos entender que, para a esquerda política, o fascismo é compreendido como um conceito completamente divorciado do seu significado original. Para um militante de esquerda, fascista é todo aquele que defende posicionamentos contrários ao progressismo, não se referindo necessariamente a um fascista clássico.
Mas, seja como for, é necessário entender que — como qualquer ideologia política — até mesmo o fascismo clássico tem o direito de existir e ocupar o seu devido lugar; portanto, fascistas não devem ser arbitrariamente censurados, apesar de defenderem conceitos que representam uma completa antítese de tudo aquilo que é valioso para os entusiastas da liberdade.
Em um país como o Brasil, onde socialistas e comunistas tem total liberdade para se expressar, defender suas ideologias e até mesmo formar partidos políticos, não faz absolutamente o menor sentido que fascistas — e até mesmo nazistas assumidos — sofram qualquer tipo de discriminação. Embora socialistas e comunistas se sintam moralmente superiores aos fascistas (ou a qualquer outra filosofia política ou escola de pensamento), sabemos perfeitamente que o seu senso de superioridade é fruto de uma pueril romantização universitária da sua própria ideologia. A história mostra efetivamente que o socialismo clássico e o comunismo causaram muito mais destruição do que o fascismo.
Portanto, se socialistas e comunistas tem total liberdade para se expressar, não existe a menor razão para que fascistas não usufruam dessa mesma liberdade.
É claro, nesse ponto, seremos invariavelmente confrontados por um oportuno dilema — o famoso paradoxo da intolerância, de Karl Popper. Até que ponto uma sociedade livre e tolerante deve tolerar a intolerância (inerente a ideologias totalitárias)?
As leis de propriedade privada resolveriam isso em uma sociedade livre. O mais importante a levarmos em consideração no atual contexto, no entanto — ao defender ou criticar uma determinada ideologia, filosofia ou escola de pensamento —, é entender que, seja ela qual for, ela tem o direito de existir. E todas as pessoas que a defendem tem o direito de defendê-la, da mesma maneira que todos os seus detratores tem o direito de criticá-la.
Essa é uma forte razão para jamais apoiarmos a censura. Muito pelo contrário, devemos repudiar com veemência e intransigência toda e qualquer forma de censura, especialmente a estatal.
Existem duas fortes razões para isso:
A primeira delas é a volatilidade da censura (especialmente a estatal). A censura oficial do governo, depois que é implementada, torna-se absolutamente incontrolável. Hoje, ela pode estar apontada para um grupo de pessoas cujas ideias divergem das suas. Mas amanhã, ela pode estar apontada justamente para as ideias que você defende. É fundamental, portanto, compreendermos que a censura estatal é incontrolável. Sob qualquer ponto de vista, é muito mais vantajoso que exista uma vasta pluralidade de ideias conflitantes na sociedade competindo entre si, do que o estado decidir que ideias podem ser difundidas ou não.
Além do mais, libertários e anarcocapitalistas não podem nunca esperar qualquer tipo de simpatia por parte das autoridades governamentais. Para o estado, seria infinitamente mais prático e vantajoso criminalizar o libertarianismo e o anarcocapitalismo — sob a alegação de que são filosofias perigosas difundidas por extremistas radicais que ameaçam o estado democrático de direito — do que o fascismo ou qualquer outra ideologia centralizada em governos burocráticos e onipotentes. Portanto, defender a censura, especialmente a estatal, representa sempre um perigo para o próprio indivíduo, que mais cedo ou mais tarde poderá ver a censura oficial do sistema se voltar contra ele.
Outra razão pela qual libertários jamais devem defender a censura, é porque — ao contrário dos estatistas — não é coerente que defensores da liberdade se comportem como se o estado fosse o seu papai e o governo fosse a sua mamãe. Não devemos terceirizar nossas próprias responsabilidades, tampouco devemos nos comportar como adultos infantilizados. Assumimos a responsabilidade de combater todas as ideologias e filosofias que agridem a liberdade e os seres humanos. Não procuramos políticos ou burocratas para executar essa tarefa por nós.
Portanto, se você ver um fascista sendo censurado nas redes sociais ou em qualquer outro lugar, assuma suas dores. Sinta-se compelido a defendê-lo, mostre aos seus detratores que ele tem todo direito de se expressar, como qualquer pessoa. Você não tem obrigação de concordar com ele ou apreciar as ideias que ele defende. Mas silenciar arbitrariamente qualquer pessoa não é uma pauta que honra a liberdade.
Se você não gosta de estado, planejamento central, burocracia, impostos, tarifas, políticas coletivistas, nacionalistas e desenvolvimentistas, mostre com argumentos coesos e convincentes porque a liberdade e o livre mercado são superiores a todos esses conceitos. Mas repudie a censura com intransigência e mordacidade.
Em primeiro lugar, porque você aprecia e defende a liberdade de expressão para todas as pessoas. E em segundo lugar, por entender perfeitamente que — se a censura eventualmente se tornar uma política de estado vigente entre a sociedade — é mais provável que ela atinja primeiro os defensores da liberdade do que os defensores do estado.
Machismo
Muitos elementos do comportamento masculino que hoje são atacados com virulência e considerados machistas pelo movimento progressista são na verdade manifestações naturais intrínsecas ao homem, que nossos avôs cultivaram ao longo de suas vidas sem serem recriminados por isso. Com a ascensão do feminismo, do progressismo e a eventual problematização do sexo masculino, o antagonismo militante dos principais líderes da revolução sexual da contracultura passou a naturalmente condenar todos os atributos genuinamente masculinos, por considerá-los símbolos de opressão e dominação social.
Apesar do Brasil ser uma sociedade liberal ultra-progressista, onde o estado protege mais as mulheres do que as crianças — afinal, a cada semana novas leis são implementadas concedendo inúmeros privilégios e benefícios às mulheres, aos quais elas jamais teriam direito em uma sociedade genuinamente machista e patriarcal —, a esquerda política persiste em tentar difundir a fantasia da opressão masculina e o mito de que vivemos em uma sociedade machista e patriarcal.
Como sempre, a realidade mostra um cenário muito diferente daquilo que é pregado pela militância da terra da fantasia. O Brasil atual não tem absolutamente nada de machista ou patriarcal. No Brasil, mulheres podem votar, podem ocupar posições de poder e autoridade tanto na esfera pública quanto em companhias privadas, podem se candidatar a cargos políticos, podem ser vereadoras, deputadas, governadoras, podem ser proprietárias do próprio negócio, podem se divorciar, podem dirigir, podem comprar armas, podem andar de biquíni nas praias, podem usar saias extremamente curtas, podem ver programas de televisão sobre sexo voltados única e exclusivamente para o público feminino, podem se casar com outras mulheres, podem ser promíscuas, podem consumir bebidas alcoólicas ao ponto da embriaguez, e podem fazer praticamente tudo aquilo que elas desejarem. No Brasil do século XXI, as mulheres são genuinamente livres para fazer as próprias escolhas em praticamente todos os aspectos de suas vidas. O que mostra efetivamente que a tal opressão do patriarcado não existe.
O liberalismo social extremo do qual as mulheres usufruem no Brasil atual — e que poderíamos estender a toda a sociedade contemporânea ocidental — é suficiente para desmantelar completamente a fábula feminista da sociedade patriarcal machista e opressora, que existe única e exclusivamente no mundinho de fantasias ideológicas da esquerda progressista.
Tão importante quanto, é fundamental compreender que nenhum homem é obrigado a levar o feminismo a sério ou considerá-lo um movimento social e político legítimo. Para um homem, ser considerado machista ou até mesmo assumir-se como um não deveria ser um problema. O progressismo e o feminismo — com o seu nefasto hábito de demonizar os homens, bem como todos os elementos inerentes ao comportamento e a cultura masculina — é que são o verdadeiro problema, conforme tentam modificar o homem para transformá-lo em algo que ele não é nem deveria ser: uma criatura dócil, passiva e submissa, que é comandada por ideologias hostis e antinaturais, que não respeitam a hierarquia de uma ordem social milenar e condições inerentes à própria natureza humana. Com o seu hábito de tentar modificar tudo através de leis e decretos, o feminismo e o progressismo mostram efetivamente que o seu real objetivo é criminalizar a masculinidade.
A verdade é que — usufruindo de um nível elevado de liberdades — não existe praticamente nada que a mulher brasileira do século XXI não possa fazer. Adicionalmente, o governo dá as mulheres uma quantidade tão avassaladora de vantagens, privilégios e benefícios, que está ficando cada vez mais difícil para elas encontrarem razões válidas para reclamarem da vida. Se o projeto de lei que pretende fornecer um auxílio mensal de mil e duzentos reais para mães solteiras for aprovado pelo senado, muitas mulheres que tem filhos não precisarão nem mesmo trabalhar para ter sustento. E tantas outras procurarão engravidar, para ter direito a receber uma mesada mensal do governo até o seu filho completar a maioridade.
O que a militância colorida da terra da fantasia convenientemente ignora — pois a realidade nunca corresponde ao seu conto de fadas ideológico — é que o mundo de uma forma geral continua sendo muito mais implacável com os homens do que é com as mulheres. No Brasil, a esmagadora maioria dos suicídios é praticada por homens, a maioria das vítimas de homicídio são homens e de cada quatro moradores de rua, três são homens. Mas é evidente que uma sociedade liberal ultra-progressista não se importa com os homens, pois ela não é influenciada por fatos concretos ou pela realidade. Seu objetivo é simplesmente atender as disposições de uma agenda ideológica, não importa quão divorciadas da realidade elas são.
O nível exacerbado de liberdades sociais e privilégios governamentais dos quais as mulheres brasileiras usufruem é suficiente para destruir a fantasiosa fábula da sociedade machista, opressora e patriarcal. Se as mulheres brasileiras não estão felizes, a culpa definitivamente não é dos homens. Se a vasta profusão de liberdades, privilégios e benefícios da sociedade ocidental não as deixa plenamente saciadas e satisfeitas, elas podem sempre mudar de ares e tentar uma vida mais abnegada e espartana em países como Irã, Paquistão ou Afeganistão. Quem sabe assim elas não se sentirão melhores e mais realizadas?
Homofobia
Quando falamos em homofobia, entramos em uma categoria muito parecida com a do racismo: o direito de discriminação é totalmente válido. Absolutamente ninguém deve ser obrigado a aceitar homossexuais ou considerar o homossexualismo como algo normal. Sendo cristão, não existe nem sequer a mais vaga possibilidade de que algum dia eu venha a aceitar o homossexualismo como algo natural. O homossexualismo se qualifica como um grave desvio de conduta e um pecado contra o Criador.
A Bíblia proíbe terminantemente conduta sexual imoral, o que — além do homossexualismo — inclui adultério, fornicação, incesto e bestialidade, entre outras formas igualmente pérfidas de degradação.
Segue abaixo três passagens bíblicas que proíbem terminantemente a conduta homossexual:
“Não te deitarás com um homem como se deita com uma mulher. Isso é abominável!” (Levítico 18:22 — King James Atualizada)
“Se um homem se deitar com outro homem, como se deita com mulher, ambos terão praticado abominação; certamente serão mortos; o seu sangue estará sobre eles.” (Levítico 20:13 — João Ferreira de Almeida Atualizada)
“O quê! Não sabeis que os injustos não herdarão o reino de Deus? Não sejais desencaminhados. Nem fornicadores, nem idólatras, nem adúlteros, nem homens mantidos para propósitos desnaturais, nem homens que se deitam com homens, nem ladrões, nem gananciosos, nem beberrões, nem injuriadores, nem extorsores herdarão o reino de Deus.” (1 Coríntios 6:9,10 —Tradução do Novo Mundo das Escrituras Sagradas com Referências)
Se você não é religioso, pode simplesmente levar em consideração o argumento do respeito pela ordem natural. A ordem natural é incondicional e incisiva com relação a uma questão: o complemento de tudo o que existe é o seu oposto, não o seu igual. O complemento do dia é a noite, o complemento da luz é a escuridão, o complemento da água, que é líquida, é a terra, que é sólida. E como sabemos o complemento do macho — de sua respectiva espécie — é a fêmea.
Portanto, o complemento do homem, o macho da espécie humana, é naturalmente a mulher, a fêmea da espécie humana. Um homem e uma mulher podem naturalmente se reproduzir, porque são um complemento biológico natural. Por outro lado, um homem e outro homem são incapazes de se reproduzir, assim como uma mulher e outra mulher.
Infelizmente, o mundo atual está longe de aceitar como plenamente estabelecida a ordem natural pelo simples fato dela existir, visto que tentam subvertê-la a qualquer custo, não importa o malabarismo intelectual que tenham que fazer para justificar os seus pontos de vista distorcidos e antinaturais. A libertinagem irrefreável e a imoralidade bestial do mundo contemporâneo pós-moderno não reconhecem nenhum tipo de limite. Quem tenta restabelecer princípios morais salutares é imediatamente considerado um vilão retrógrado e repressivo, sendo ativamente demonizado pela militância do hedonismo, da luxúria e da licenciosidade desenfreada e sem limites.
Definitivamente, fazer a apologia da moralidade, do autocontrole e do autodomínio não faz nenhum sucesso na Sodoma e Gomorra global dos dias atuais. O que faz sucesso é lacração, devassidão, promiscuidade e prazeres carnais vazios. O famoso escritor e filósofo francês Albert Camus expressou uma verdade contundente quando disse: “Uma só frase lhe bastará para definir o homem moderno — fornicava e lia jornais”.
Qualquer indivíduo tem o direito inalienável de discriminar ativamente homossexuais, pelo direito que ele julgar mais pertinente no seu caso. A objeção de consciência para qualquer situação é um direito natural dos indivíduos. Há alguns anos, um caso que aconteceu nos Estados Unidos ganhou enorme repercussão internacional, quando o confeiteiro Jack Phillips se recusou a fazer um bolo de casamento para o “casal” homossexual Dave Mullins e Charlie Craig.
Uma representação dos direitos civis do estado do Colorado abriu um inquérito contra o confeiteiro, alegando que ele deveria ser obrigado a atender todos os clientes, independente da orientação sexual, raça ou crença. Preste atenção nas palavras usadas — ele deveria ser obrigado a atender.
Como se recusou bravamente a ceder, o caso foi parar invariavelmente na Suprema Corte, que decidiu por sete a dois em favor de Jack Phillips, sob a alegação de que obrigar o confeiteiro a atender o “casal” homossexual era uma violação nefasta dos seus princípios religiosos. Felizmente, esse foi um caso em que a liberdade prevaleceu sobre a tirania progressista.
Evidentemente, homossexuais não devem ser agredidos, ofendidos, internados em clínicas contra a sua vontade, nem devem ser constrangidos em suas liberdades pelo fato de serem homossexuais. O que eles precisam entender é que a liberdade é uma via de mão dupla. Eles podem ter liberdade para adotar a conduta que desejarem e fazer o que quiserem (contanto que não agridam ninguém), mas da mesma forma, é fundamental respeitar e preservar a liberdade de terceiros que desejam rejeitá-los pacificamente, pelo motivo que for.
Afinal, ninguém tem a menor obrigação de aceitá-los, atendê-los ou sequer pensar que uma união estável entre duas pessoas do mesmo sexo — incapaz de gerar descendentes, e, portanto, antinatural — deva ser considerado um matrimônio de verdade. Absolutamente nenhuma pessoa, ideia, movimento, crença ou ideologia usufrui de plena unanimidade no mundo. Por que o homossexualismo deveria ter tal privilégio?
Homossexuais não são portadores de uma verdade definitiva, absoluta e indiscutível, que está acima da humanidade. São seres humanos comuns que — na melhor das hipóteses —, levam um estilo de vida que pode ser considerado “alternativo”, e absolutamente ninguém tem a obrigação de considerar esse estilo de vida normal ou aceitável. A única obrigação das pessoas é não interferir, e isso não implica uma obrigação em aceitar.
Discriminar homossexuais (assim como pessoas de qualquer outro grupo, raça, religião, nacionalidade ou etnia) é um direito natural por parte de todos aqueles que desejam exercer esse direito. E isso nem o direito positivo nem a militância progressista poderão algum dia alterar ou subverter. O direito natural e a inclinação inerente dos seres humanos em atender às suas próprias disposições é simplesmente imutável e faz parte do seu conjunto de necessidades.
Conclusão
A militância progressista é absurdamente autoritária, e todas as suas estratégias e disposições ideológicas mostram que ela está em uma guerra permanente contra a ordem natural, contra a liberdade e principalmente contra o homem branco, cristão, conservador e tradicionalista — possivelmente, aquilo que ela mais odeia e despreza.
Nós não podemos, no entanto, ceder ou dar espaço para a agenda progressista, tampouco pensar em considerar como sendo normais todas as pautas abusivas e tirânicas que a militância pretende estabelecer como sendo perfeitamente razoáveis e aceitáveis, quer a sociedade aceite isso ou não. Afinal, conforme formos cedendo, o progressismo tirânico e totalitário tende a ganhar cada vez mais espaço.
Quanto mais espaço o progressismo conquistar, mais corroída será a liberdade e mais impulso ganhará o totalitarismo. Com isso, a cultura do cancelamento vai acabar com carreiras, profissões e com o sustento de muitas pessoas, pelo simples fato de que elas discordam das pautas universitárias da moda.
A história mostra perfeitamente que quanto mais liberdade uma sociedade tem, mais progresso ela atinge. Por outro lado, quanto mais autoritária ela for, mais retrocessos ela sofrerá. O autoritarismo se combate com liberdade, desafiando as pautas de todos aqueles que persistem em implementar a tirania na sociedade. O politicamente correto é o nazismo dos costumes, que pretende subverter a moral através de uma cultura de vigilância policial despótica e autoritária, para que toda a sociedade seja subjugada pela agenda totalitária progressista.
Pois quanto a nós, precisamos continuar travando o bom combate em nome da liberdade. E isso inclui reconhecer que ideologias, hábitos e costumes de que não gostamos tem o direito de existir e até mesmo de serem defendidos.
-
 @ bf47c19e:c3d2573b
2025-05-27 14:54:03
@ bf47c19e:c3d2573b
2025-05-27 14:54:03Originalni tekst na bitcoin-balkan.com.
Pregled sadržaja
- 5 Razloga Zašto je Novac Važan za Vas, Individualno
- 3 Razloga Zašto je Novac Važan za Društvo u Celini
- Zašto ljudi mrze novac?

Novac vs trenuci – da li oni treba da budu u sukobu? Kakva je uloga novca?
Novac je nepredvidiva zver modernog društva – neki ga veličaju sa stalnom željom da steknu više, dok ga drugi demonizuju i kažu da je pohlepa srž društvenih problema. Tokom mnogih godina svog života, ja sam često prelazio sa jednog na drugo gledište, i naučio mnogo toga upoznajući druge ljude koji žive na oba kraja ovog spektra. Kao i kod mnogih složenih tema, istina leži negde u sredini.
Novac je važan zato što on može da pomogne u uklanjanju materijalnih želja i patnji – omogućavanjem da preuzmete kontrolu nad svojim životom i da brinete o voljenima. Novac podiže životni standard društva omogućavanjem trgovine, a pritom minimalizuje potrebu za poverenjem.
Na novac možemo gledati kao na način da svoj uloženi trud sačuvamo u odredjenom obliku, i da ga vremenom prenesemo, tako da možemo da uživamo u plodovima svog rada. Novac kao alat je jedna od najvažnijih stvari za rast civilizacije. Na nesreću, mnogi su vremenom zlostavljali novac, ali sa dobrim razlogom: način na koji naš novac danas funkcioniše dovodi do duboko podeljenog društva – što ću i objasniti.
5 Razloga Zašto je Novac Važan za Vas, Individualno
Novac je važan za rast bogatstva, što je malo drugačije od toga da imamo veliku platu ili jednostavno zarađivati velike količine novca. Bogatstvo je otklanjanje želja, kako bi mogli da obratimo više pažnje na neke korisnije stvari u životu, od pukog preživljavanja i osnovnih udobnosti.
Bogata osoba je ona koja zaradi više novca nego što potroši, i koja ga čuva – ona čuva svoj rad tokom vremena. Uporedite ovo sa visoko plaćenim lekarom koji živi u velikoj vili sa hipotekom i sa Mercedesom na lizing. Iako ova osoba ima visoke prihode, ona takođe ima velike rashode u vidu obaveze plaćanja te hipoteke i lizinga. Te obaveze sprečavaju ovu osobu da uživa u istinskim blagodetima novca i bogatstva koje one predstavljaju:
1. Sloboda od potrebe za radom
Bez bogatstva, vi morate da radite da biste preživeli. Dostizanjem bogatstva i odredjenom imovinom koja vam donosi novac bez potrebe da vi trošite svoje vreme, vi možete da oslobodite svoj raspored. Više ne zavisite od posla koji mrzite, i nemorate da provodite 40 sati nedeljno odvojeni od porodice, samo da biste se pobrinuli za svoje osnovne potrebe. Dobijanje otkaza u padu ekonomije neće vas dovesti do finansijske propasti ili nečeg goreg.
2. Kontrola nad time kako vi trošite svoje vreme
Kada steknete bogatstvo, vi možete da odlučite kako želite da provodite svoje vreme. Kada se nalazimo u trci pacova i radimo 40+ sati nedeljno, često se naviknemo da novac trošimo onda kada imamo slobodnog vremena. Idemo na lepe večere ili idemo na skupe odmore. Međutim, sa više vremena, a možda čak i sa manje novca, mi možemo da imamo isto ili više uživanja živeći usporenije.
Razmislite o ovome – ukoliko imate samo 1 nedelju slobodno od posla, vi onda morate da kupite onaj mnogo skuplji let u Petak uveče koji se vraća u sledeću Nedelju, kako biste maksimalno iskoristili svoje vreme na nekom egzotičnom mestu za odmor. Međutim, ukoliko ste u mogućnosti da izdržavate sebe bez potrebe da mnogo vremena provodite na poslu, vi onda možete u Utorak da krenete jeftinijim letom i vratite se u sledeću Sredu. Takođe nećete osećati toliki pritisak da se opustite u uživanju tokom vaše nedelje u inostranstvu – možda ćete čak moći i da ostanete duže i da istražujete više, bez plaćanja skupih turističkih agencija i hotela kako bi organizovali vaše kraće putovanje.
3. Sposobnost da pomažete vašim prijateljima i porodici
Onda kada novca imate na pretek, možete poboljšati svoje odnose sa prijateljima i porodicom ne samo kroz dodatno slobodno vreme koje provodite sa njima, već i sa samim novcem. Ako je vašem prijatelju potrebna hitna operacija, vi možete da mu izadjete u susret i pomognete mu da stane na svoje noge. Ukoliko vam je tetka bolesna, vi možete da provedete vreme pored nje, umesto da je pozovete na kratko dok putujete prema kući vraćajući se nakon celog dana provedenog u kancelariji.
4. Smanjen finansijski stres
Stres je sveobuhvatno i opasno stanje modernog doba, sa kojim gotovo svi mi živimo u nekoj odredjenoj meri. Povezan je sa lošim zdravljem, sa preko 43% svih odraslih koji kažu da pate od odredjenih zdravstvenih problema uzrokovanih stresom. Stres zbog posla pogađa 83% zaposlenih.
Pravo bogatstvo – koje znači eliminaciju želja i potreba – može da ukloni ovaj stres i njegove negativne uticaje na druge delove života. Ovo bi čak moglo da ukloni većinu stresa u vašem životu, uzimajući u obzir da je uzrok stresa broj 1 upravo novac.
5. Bolje možete da pomognete vašoj zajednici
Mnogi od nas žele da volontiraju u svojim zajednicama i pomognu onima koja je pomoć preko potrebna, ali nisu u stanju da pronađu slobodnog vremena i energije zbog svog posla, porodice i društvenih aktivnosti koje nas mentalno i fizički čine srećnima, zdravima i hranjenima. Sa bogatstvom, mi možemo da posvetimo vreme koje nam je potrebno za razumevanje i doprinos drugima – a ne samo da sa vremena na vreme pomognemo slanjem humanitarnog SMS-a.
Novac, koji se pametno koristi, je moćno sredstvo za poboljšanje vašeg života i života vaših najmilijih i zajednice. Međutim, novac je takođe moćno sredstvo za poboljšanje društva u celini – ukoliko je dobro strukturiran.
3 Razloga Zašto je Novac Važan za Društvo u Celini
Novac poboljšava sposobnost ljudi da trguju jedni s drugima, što podstiče određene specijalizacije. Ako je imanje vašeg komšije odlično za proizvodnju vina, a vaše je pogodno za žito, obojica možete da profitirate trgovinom. Sad oboje imate i hleb i vino, umesto jednog pijanog vlasnika vinograda i jednog proizvodjača žita kome je dosadno!
Novac poboljšava društvo na nekoliko načina:
1. Omogućava specijalizaciju
Kao u primeru vlasnika vinograda i proizvodjača žita, novac omogućava povećanu specijalizaciju poboljšavajući sposobnost trgovine. Svaka razmena dobara ima problem sa ‘sticajima potreba’ – oba partnera u trgovini moraju da žele ono što druga osoba ima da bi pristala na trgovinu.
Možemo da mislimo o novcu kao o dobru koje žele gotovo svi. Ovo trgovinu čini mnogo jednostavnijom – da biste stekli odredjeno dobro, sve što vam je potrebno je novac, a ne neka slučajna stvar koju prodavac tog dobra takođe želi u tom trenutku. Vremenom je upotreba novca omogućila specijalizaciju, što je povećalo kvalitet i složenost roba i usluga.
Zamislite da sami pokušate da napravite svoj telefon – a bili su potrebni milioni stručnjaka i specijalizovana oprema da bi proizveli taj uređaj. Svi ti stručnjaci i kompanije plaćaju jedni drugima u novcu, omogućavajući složenom plesu globalnih proizvođača i lanaca snabdevanja da taj telefon isporuče na dlan vaše ruke. Čak i nešto tako jednostavno kao flaša za vodu uključuje naftna polja i proizvodne pogone koji su možda hiljadama kilometara od vaše kuće.
Kada ljudi mogu da se specijalizuju, kvalitet robe i usluga može da se poveća.
2. Omogućava korisnu trgovinu uz smanjeno poverenje
Mala društva mogu mirno i produktivno da posluju bez novca koristeći usluge, “dodjem ti” i uzajamno razumevanje. Međutim, kako se društva uvećavaju, svima brzo postaje nemoguće da održavaju lične odnose i isti stepen poverenja sa svima ostalima. Sistem trgovine uslugama i međusobnog poverenja ne funkcioniše previše dobro sa putnikom koji se nalazi na proputovanju kroz grad, i provede samo 15 minuta svog života u vašoj prodavnici.
Novac minimizira poverenje potrebno za trgovinu u većim društvima. Sada više ne moram da verujem da ćete mi pomoći kasnije kada mi zatreba – mogu samo da prihvatim uplatu od vas i da to koristim da bih sebi pomogao kasnije. Jedan od mojih omiljenih mislilaca, Nick Szabo, ovo naziva ‘društvena prilagodljivost’.
3. Smanjuje upotrebu sile
Kada društvo teži upotrebi određenog oblika novca za olakšavanje trgovine, može u velikoj meri da smanji nasilje u tom društvu. Kako to može biti tako? Zar ljudi ne bi i dalje želeli da kradu jedni od drugih ili da se svete?
Ukoliko razmišljamo van uobičajnih okvira, možemo da počnemo da razumemo kako novac može da smanji nasilje. Ako ti i ja živimo u susednim zemljama i želimo nešto što druga zemlja ima, imamo dva načina da to dobijemo: uzimanjem na silu ili menjanjem nečeg našeg za to. Kao što je ranije rečeno, novac znatno olakšava trgovinu – pa ćemo postojanjem zajedničkog monetarnog sistema verovatnije radje izvršiti trgovinu nego napad na zemlju. Zašto bismo rizikovali svoje živote kad možemo samo mirno da trgujemo jedni sa drugima?
Zašto ljudi mrze novac?
Pa ako novac ima toliko koristi za nas lično i za društvo u celini, zašto toliko ljudi mrzi novac? Zašto je demonizovan, zajedno sa onima koji ga imaju puno?
Za deo ovoga može biti okrivljen problem u jednakosti mogućnosti – to da je nekima teže da izadju iz nemaštine i postanu bogati. Bez sumnje, neki mali deo potiče od ljudi koji jednostavno ne žele da se trude ili preduzmu neophodne rizike da bi postali bogati.
Međutim, oba ova problema imaju više veze sa problemima kako naš novac danas funkcioniše, nego sa bilo kojim problemom u samom konceptu novca. Novčani sistem treba da nagrađuje ljude koji proizvode vredne stvari i trguju njima sa drugima. Verujem da većina ljudi danas misli da novac tako funkcioniše, i to ne bi smelo da bude daleko od istine.
Naš trenutni monetarni sistem, na žalost, nagrađuje ’finansijalizaciju’ – pretvarajući sve u imovinu, čija vrednost može da se napumpava ili spušta stvaranjem dobre priče i navođenjem drugih da veruju u nju. Razuzdani dug pogonjen stalnim omalovažavanjem svih glavnih valuta dodat je ovom blatu finansijalizacije. Sada je isplativije podići ogroman kredit i koristiti ga za brzo okretanje imovine radi zarade nego izgraditi posao koji društvu nudi korisne robe i usluge.
Tradicionalni monetarni sistem dodatno nagradjuje predatore, partnere u zločinu i neradnike.
Propast našeg novca razvila se tokom proteklih pola veka, počevši od toga kada su naše valute postale ništa više od parčeta papira, podržanog sa verom i kreditima naših vlada. Da biste bolje razumeli ovu promenu, pogledajte moj post o svrsi i istoriji novca.
Ako vam se sviđa moj rad, molim vas da ga podelite sa svojim prijateljima i porodicom. Cilj mi je da svima pružim pogled u ekonomiju i na to kako ona utiče na njihov život.
-
 @ 33baa074:3bb3a297
2025-05-28 08:25:13
@ 33baa074:3bb3a297
2025-05-28 08:25:13The oil-in-water sensoris an instrument specially used to detect oil substances in water bodies. Its working principle is mainly based on the characteristic that oil substances will produce fluorescence under ultraviolet light. The following is a detailed explanation:
Principle Overview The oil-in-water sensor uses the characteristic that oil substances will produce fluorescence under ultraviolet light, and measures the fluorescence intensity to infer the concentration of oil substances. Specifically, the sensor uses ultraviolet light as the excitation light source to irradiate the water sample to be tested. After the oil substance absorbs ultraviolet light, it will stimulate fluorescence, and the fluorescence signal is received by the photo detector and converted into an electrical signal. By measuring the strength of the electrical signal, the concentration of oil substances in the water sample can be inferred.
Workflow Ultraviolet light irradiation: The ultraviolet light source inside the sensor emits ultraviolet light and irradiates it into the water sample to be tested.
Fluorescence generation: After the oil substance in the water sample absorbs ultraviolet light, it will stimulate fluorescence.
Fluorescence detection: The photo detector in the sensor measures the intensity of this fluorescence.
Signal conversion: The signal processing circuit converts the output of the photo detector into an electrical signal proportional to the amount of oil in the water. Data analysis: By analyzing the strength of the electrical signal, the concentration of oil substances in the water sample can be obtained.
Features and applications The oil in water sensor has high sensitivity and can detect soluble and falsifiable oils. It is suitable for a variety of water quality monitoring scenarios, such as oil field monitoring, industrial circulating water, condensate water, wastewater treatment, surface water stations, etc. In addition, it can also monitor the content of crude oil (benzene and benzene homologous) in water sources such as reservoirs and water plants in real time online, play an early warning role, and protect the safety of water sources.
Practical application The oil in water sensor has a wide range of functions in practical applications, including but not limited to the following aspects: Monitoring the water quality of water sources: ensuring the safety of drinking water, and timely discovering pollution sources and ensuring water supply safety by continuously monitoring oil substances in water sources. Monitoring sewage treatment plant emissions: ensuring that the discharge water quality of sewage treatment plants meets the emission standards to avoid secondary pollution to the environment. Monitoring rivers, lakes and other water bodies: assessing the pollution status and providing a basis for pollution control. Early warning and emergency response: It has real-time monitoring and early warning functions, and can issue an alarm in time when abnormal conditions are found, providing valuable time for emergency response and reducing losses caused by pollution. Scientific research: Through the monitoring data of this sensor, we can deeply understand the distribution, migration and transformation of oil substances in water bodies, and provide a scientific basis for environmental protection and governance.
In summary, the oil in water sensor monitors the oil content in water bodies through ultraviolet fluorescence method, has high sensitivity and broad application prospects, and is an indispensable and important tool in modern environmental monitoring and industrial production.
-
 @ 45d6c2bf:56915a25
2025-05-27 14:23:39
@ 45d6c2bf:56915a25
2025-05-27 14:23:39published without nostr installed
-
 @ 43baaf0c:d193e34c
2025-05-27 14:08:02
@ 43baaf0c:d193e34c
2025-05-27 14:08:02During the incredible Bitcoin Filmfest, I attended a community session where a discussion emerged about zapping and why I believe zaps are important. The person leading the Nostr session who is also developing an app that’s partially connected to Nostr mentioned they wouldn’t be implementing the zap mechanism directly. This sparked a brief but meaningful debate, which is why I’d like to share my perspective as an artist and content creator on why zaps truly matter.
Let me start by saying that I see everything from the perspective of an artist and creator, not so much from a developer’s point of view. In 2023, I started using Nostr after spending a few years exploring the world of ‘shitcoins’ and NFTs, beginning in 2018. Even though I became a Bitcoin maximalist around 2023, those earlier years taught me an important lesson: it is possible to earn money with my art.
Whether you love or hate them, NFTs opened my eyes to the idea that I could finally take my art to the next level. Before that, for over 15 years, I ran a travel stock video content company called @traveltelly. You can read the full story about my journey in travel and content here: https://yakihonne.com/article/traveltelly@primal.net/vZc1c8aXrc-3hniN6IMdK
When I truly understood what Bitcoin meant to me, I left all other coins behind. Some would call that becoming a Bitcoin maximalist.
The first time I used Nostr, I discovered the magic of zapping. It amazed me that someone who appreciates your art or content could reward you—not just with a like, but with real value: Bitcoin, the hardest money on earth. Zaps are small amounts of Bitcoin sent as a sign of support or appreciation. (Each Bitcoin is divisible into 100 million units called Satoshis, or Sats for short—making a Satoshi the smallest unit of Bitcoin recorded on the blockchain.)
 The Energy of Zaps
The Energy of ZapsIf you’re building an app on Nostr—or even just connecting to it—but choose not to include zaps, why should artists and content creators share their work there? Why would they leave platforms like Instagram or Facebook, which already benefit from massive network effects?
Yes, the ability to own your own data is one of Nostr’s greatest strengths. That alone is a powerful reason to embrace the protocol. No one can ban you. You control your content. And the ability to post once and have it appear across multiple Nostr clients is an amazing feature.
But for creators, energy matters. Engagement isn’t just about numbers—it’s about value. Zaps create a feedback loop powered by real appreciation and real value, in the form of Bitcoin. They’re a signal that your content matters. And that energy is what makes creating on Nostr so special.
But beyond those key elements, I also look at this from a commercial perspective. The truth is, we still can’t pay for groceries with kisses :)—we still need money as a medium of exchange. Being financially rewarded for sharing your content gives creators a real incentive to keep creating and sharing. That’s where zaps come in—they add economic value to engagement.
A Protocol for Emerging Artists and Creators
I believe Nostr offers a great starting point for emerging artists and content creators. If you’re just beginning and don’t already have a large following on traditional social media platforms, Nostr provides a space where your work can be appreciated and directly supported with Bitcoin, even by a small but engaged community.
On the other hand, creators who already have a big audience and steady income on platforms like Instagram or YouTube may not feel the urgency to switch. This is similar to how wealthier countries are often slower to understand or adopt Bitcoin—because they don’t need it yet. In contrast, people in unbanked regions or countries facing high inflation are more motivated to learn how money really works.
In the same way, emerging creators—those still finding their audience and looking for sustainable ways to grow—are often more open to exploring new ecosystems like Nostr, where innovation and financial empowerment go hand in hand.
The same goes for Nostr. After using it for the past two years, I can honestly say: without Nostr, I wouldn’t be the artist I am today.
Nostr motivates me to create and share every single day. A like is nice but receiving a zap, even just 21 sats, is something entirely different. Once you truly understand that someone is willing to pay you for what you share, it’s no longer about the amount. It’s about the magic behind it. That simple gesture creates a powerful, positive energy that keeps you going.
Even with Nostr’s still relatively small user base, I’ve already been able to create projects that simply wouldn’t have been possible elsewhere.
Zaps do more than just reward—they inspire. They encourage you to keep building your community. That inspiration often leads to new projects. Sometimes, the people who zap you become directly involved in your work, or even ask you to create something specifically for them.
That’s the real value of zaps: not just micro-payments, but micro-connections sparks that lead to creativity, collaboration, and growth.
Proof of Work (PoW)
Over the past two years, I’ve experienced firsthand how small zaps can evolve into full art projects and even lead to real sales. Here are two examples that started with zaps and turned into something much bigger:
Halving 2024 Artwork
When I started the Halving 2024 project, I invited people on Nostr to be part of it. 70 people zapped me 2,100 sats each, and in return, I included their Npubs in the final artwork. That piece was later auctioned and sold to Jurjen de Vries for 225,128 Sats.
Magic Internet Money
For the Magic Internet Money artwork, I again invited people to zap 2,100 sats to be included. Fifty people participated, and their contributions became part of the final art frame. The completed piece was eventually sold to Filip for 480,000 sats.
These examples show the power of zaps: a simple, small act of appreciation can turn into larger engagement, deeper connection, and even the sale of original art. Zaps aren’t just tips—they’re a form of collaboration and support that fuel creative energy.
I hope this article gives developers a glimpse into the perspective of an artist using Nostr. Of course, this is just one artist’s view, and it doesn’t claim to speak for everyone. But I felt it was important to share my Proof of Work and perspective.
For me, Zaps matter.
Thank you to all the developers who are building these amazing apps on Nostr. Your work empowers artists like me to share, grow, and be supported through the value-for-value model.
-
 @ 33baa074:3bb3a297
2025-05-28 08:10:17
@ 33baa074:3bb3a297
2025-05-28 08:10:17The control of residual chlorine in swimming pools is an important part of water quality management, which aims to ensure the sanitation and safety of swimming pool water while avoiding discomfort to swimmers. Here are some key points about residual chlorine control in swimming pools:
Standards for residual chlorine According to the regulations of the national health supervision department, the residual chlorine in swimming pool water should be kept between 0.3mg/L-1.5mg/L. This range can not only ensure effective disinfection, but also avoid irritation to swimmers' skin and eyes caused by excessive residual chlorine. Too low residual chlorine will lead to incomplete disinfection and increase the risk of bacterial growth; while too high residual chlorine may cause human discomfort and even poisoning.
 The role of residual chlorine
Residual chlorine is a residual disinfectant in swimming pool water, usually in the form of sodium hypocrite (NaClO). It has strong oxidizing properties and can effectively kill bacteria, viruses and other microorganisms in water, thereby ensuring the health of swimmers. In addition, residual chlorine can eliminate harmful substances such as organic matter and ammonia in water to keep the water clean.
The role of residual chlorine
Residual chlorine is a residual disinfectant in swimming pool water, usually in the form of sodium hypocrite (NaClO). It has strong oxidizing properties and can effectively kill bacteria, viruses and other microorganisms in water, thereby ensuring the health of swimmers. In addition, residual chlorine can eliminate harmful substances such as organic matter and ammonia in water to keep the water clean.Residual chlorine detection method The method of detecting residual chlorine in swimming pools usually uses test strips or test kits for qualitative or quantitative detection. In addition, online monitoring instruments can be used to monitor the residual chlorine in the swimming pool in real time. These methods can help managers promptly detect and deal with situations where the residual chlorine content is too high or too low, ensuring that the water quality of the swimming pool meets the standards.
Methods for controlling residual chlorine Reasonable addition of disinfectants: According to the water quality of the swimming pool and the number of swimmers, reasonable addition of disinfectants to control the residual chlorine content within the specified range.
Regular testing: Regularly test the residual chlorine in the swimming pool to promptly detect and deal with situations where the residual chlorine content is too high or too low.
Maintain swimming pool equipment: Regularly check and maintain swimming pool equipment to ensure the water treatment effect and circulation filtration are normal, and reduce residual disinfectants and other harmful substances in the water.
Do a good job in swimmer hygiene management: Strengthen swimmer hygiene management, require swimmers to shower and rinse their feet before entering the pool, and reduce pollution sources entering the swimming pool.
Solution for excessive residual chlorine If the residual chlorine content in the swimming pool exceeds the standard range, the following measures can be taken:
Use decorating agent: Use decorating agent to quickly restore the excessive residual chlorine in the swimming pool to the normal range (0.3~0.5mg/L). This method is applicable to excessive residual chlorine caused by excessive addition of chlorine disinfectant.
Adjust the water treatment process: According to the water quality, adjust the water treatment process appropriately, such as selecting the appropriate type and dosage of disinfectant, and adjusting operating parameters such as flow rate, pH value, etc., to reduce the generation of residual chlorine.
Strengthen equipment maintenance: Regularly maintain and maintain the water treatment equipment of the swimming pool to ensure its normal operation and disinfection effect.
Through the above methods, the residual chlorine content in the swimming pool can be effectively controlled to ensure water quality safety and protect the health of swimmers.
-
 @ da0b9bc3:4e30a4a9
2025-05-28 08:07:30
@ da0b9bc3:4e30a4a9
2025-05-28 08:07:30Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
https://stacker.news/items/991020
-
 @ c1e9ab3a:9cb56b43
2025-05-27 13:19:53
@ c1e9ab3a:9cb56b43
2025-05-27 13:19:53I. Introduction: Money as a Function of Efficiency and Preference
Money is not defined by law, but by power over productivity. In any open economy, the most economically efficient actors—those who control the most valuable goods, services, and knowledge—ultimately dictate the medium of exchange. Their preferences signal to the broader market what form of money is required to access the highest-value goods, from durable commodities to intangibles like intellectual property and skilled labor.
Whatever money these actors prefer becomes the de facto unit of account and store of value, regardless of its legal status. This emergent behavior is natural and reflects a hierarchy of monetary utility.
II. Classical Gresham’s Law: A Product of Market Distortion
Gresham’s Law, famously stated as:
"Bad money drives out good"
is only valid under coercive monetary conditions, specifically: - Legal tender laws that force the acceptance of inferior money at par with superior money. - Fixed exchange rates imposed by decree, not market valuation. - Governments or central banks backing elastic fiduciary media with promises of redemption. - Institutional structures that mandate debt and tax payments in the favored currency.
Under these conditions, superior money (hard money) is hoarded, while inferior money (soft, elastic, inflationary) circulates. This is not an expression of free market behavior—it is the result of suppressed price discovery and legal coercion.
Gresham’s Law, therefore, is not a natural law of money, but a law of distortion under forced parity and artificial elasticity.
III. The Collapse of Coercion: Inversion of Gresham’s Law
When coercive structures weaken or are bypassed—through technological exit, jurisdictional arbitrage, monetary breakdown, or political disintegration—Gresham’s Law inverts:
Good money drives out bad.
This occurs because: - Market actors regain the freedom to select money based on utility, scarcity, and credibility. - Legal parity collapses, exposing the true economic hierarchy of monetary forms. - Trustless systems (e.g., Bitcoin) or superior digital instruments (e.g., stablecoins) offer better settlement, security, and durability. - Elastic fiduciary media become undesirable as counterparty risk and inflation rise.
The inversion marks a return to monetary natural selection—not a breakdown of Gresham’s Law, but the collapse of its preconditions.
IV. Elasticity and Control
Elastic fiduciary media (like fiat currency) are not intrinsically evil. They are tools of state finance and debt management, enabling rapid expansion of credit and liquidity. However, when their issuance is unconstrained, and legal tender laws force their use, they become weapons of economic coercion.
Banks issue credit unconstrained by real savings, and governments enforce the use of inflated media through taxation and courts. This distorts capital allocation, devalues productive labor, and ultimately hollows out monetary confidence.
V. Monetary Reversion: The Return of Hard Money
When the coercion ends—whether gradually or suddenly—the monetary system reverts. The preferences of the productive and wealthy reassert themselves:
- Superior money is not just saved—it begins to circulate.
- Weaker currencies are rejected not just for savings, but for daily exchange.
- The hoarded form becomes the traded form, and Gresham’s Law inverts completely.
Bitcoin, gold, and even highly credible stable instruments begin to function as true money, not just stores of value. The natural monetary order returns, and the State becomes a late participant, not the originator of monetary reality.
VI. Conclusion
Gresham’s Law operates only under distortion. Its inversion is not an anomaly—it is a signal of the collapse of coercion. The monetary system then reorganizes around productive preference, technological efficiency, and economic sovereignty.
The most efficient market will always dictate the form of hard money. The State can delay this reckoning through legal force, but it cannot prevent it indefinitely. Once free choice returns, bad money dies, and good money lives again.
-
 @ 33baa074:3bb3a297
2025-05-28 07:50:06
@ 33baa074:3bb3a297
2025-05-28 07:50:06Soil moisture is a key factor that affects the structure and function of soil microbial communities. Here are some of the main aspects of how soil moisture affects microorganisms:
Affecting the Growth and Metabolism of Microorganisms Changes in soil moisture content directly affect the growth and metabolic activities of microorganisms. Under suitable moisture conditions, microorganisms are better able to carry out metabolic activities, thereby promoting the decomposition of soil organic matter and the transformation of nutrients. However, under extremely dry or overly wet conditions, the activity of microorganisms will be inhibited, resulting in a decline in soil functions.

Changing the Structure of Microbial Communities Changes in soil moisture conditions can lead to significant changes in the structure of microbial communities. For example, under drought conditions, the number of drought-tolerant microorganisms may increase to adapt to the water shortage environment. While under wet conditions, aerobic microorganisms may dominate. This change in community structure not only affects the soil's water retention capacity, but also other ecological functions of the soil.
Affecting the Stability of Soil Aggregates Soil aggregates are clumps formed by soil particles through physical, chemical and biological actions, and they have an important impact on the soil's water retention capacity. Soil microorganisms participate in the formation and stability of soil aggregates by secreting substances such as extracellular polymers. Appropriate soil moisture helps maintain the stability of soil aggregates, thereby improving the soil's water retention capacity. However, excessive moisture or drought may lead to the destruction of soil aggregates and reduce the soil's water retention capacity.
Regulating soil moisture dynamics Soil microorganisms can regulate the dynamic balance of soil moisture through their metabolic activities, such as decomposing organic matter and synthesizing exopolysaccharides. For example, some microorganisms can increase the water holding capacity of the soil by secreting exopolysaccharides, while others can release water by decomposing organic matter. These activities help maintain the stability of soil moisture and support plant growth.
Influencing the physical properties of soil Soil moisture can also indirectly affect the living environment of microorganisms by affecting the physical properties of the soil, such as pore structure and texture. Good soil pore structure is conducive to the penetration and storage of water, and also provides a suitable living space for microorganisms. Soil texture is closely related to the stability of aggregates. Sandy soils have poor aggregate stability and weak water retention capacity; while clay soils have good aggregate stability and strong water retention capacity.
In summary, soil moisture has many effects on microorganisms, including affecting the growth and metabolism of microorganisms, changing the structure of microbial communities, affecting the stability of soil aggregates, regulating soil moisture dynamics, and affecting the physical properties of soil. Therefore, maintaining suitable soil moisture conditions is of great significance for protecting the diversity and function of soil microbial communities and improving the water retention capacity of soil.
-
 @ a0e937b7:50db609a
2025-05-27 13:06:38
@ a0e937b7:50db609a
2025-05-27 13:06:38Because we are not merely addicted to #Narrativium: It is our drive, imbued into our very essence. And it is so much easier to absorb our daily dose from the billions of trickles provided by everyone else as a substitute drug #Gossipium, or temporarily saturate our unquenchable thirst by just giving in to the temptation by the incessable stream of Movies and Series providing #Fictionium than it is to find a properly satisfying Source Of Narrativium (acronymize that 😉), let alone create our own Narrativium that might even be worthy of sharing. And yet, there is so much more fulfilment possible by letting one's creativity work instead of merely using a "share" button - which briefly seems to trick the human brain into believing that one has actually participated in providing one's peers with proper Narrativium, possibly as part of an implicit social contract: "I give you all some Narrativium I found, now give me more in return". It is such a trivial action to take, even more effortless than gossiping. But let's be honest, it often just feels hollow. And even when we write something, it is again tempting to just create #Rantium instead of something actually useful.
 Gossypium herbaceum, the cotton plant (Photo by H. Zell from Wikipedia)
Gossypium herbaceum, the cotton plant (Photo by H. Zell from Wikipedia)Originally I merely wanted to post a witty quote from https://wiki.lspace.org/mediawiki/Narrativium about Narrativium on Facebook:
"Humans add narrativium to their world. They insist on interpreting the universe as if it's telling a story. This leads them to focus on facts that fit the story, while ignoring those that don't." - T. Pratchett, I. Steward, J. Cohen, The Science of Discworld I
Maybe even subtly allude to how that might explain quite a lot about the everyday insanity that seems to surround us, especially these days.
"We are not Homo sapiens, Wise Man. We are the third chimpanzee. [...] We are Pan narrans, the storytelling ape. [...] if you understand the power of story, and learn to detect abuses of it, you might actually deserve the appellation Homo sapiens." - T. Pratchett, I. Steward, J. Cohen, The Science of Discworld II
Really. I was just going to quote a bit and go on about my day with some meaningless procrastination. Why already bother with housework when I can delay that until tomorrow or the day after and just watch some series in the Arrowverse now? But after ten minutes of a Legends of Tomorrow episode called "Lucha de Apuestas", curiosity got the better of me. What is it with Luchadores and their masks, I mockingly wondered. So I read Wikipedia on it. Lots of culture, history and, most importantly to me, Narrativium. I probably couldn't care less for to guys bumping fists on a stage, I don't really care about watching any sports either. But there's a certain fascination to stories, isn't there? So I felt like sharing about Narrativium, and here we are.
—
That's it for now, I might keep writing on this. One day. Just as I keep continuing writing everything else I start. Not. Well, motivate me.
-
 @ 33baa074:3bb3a297
2025-05-28 07:27:02
@ 33baa074:3bb3a297
2025-05-28 07:27:02Distilled water has a wide range of applications in the medical field, mainly including the following aspects: Preparation of injection water Distilled water is an indispensable agent in medical institutions, used for the preparation of drugs, injection and washing of instruments, etc. In the medical process, sterile injection water is needed to flush wounds, prepare drugs, etc. The distilled water machine can ensure the purity of water and prevent microorganisms and harmful substances in the water from causing harm to patients.
Surgical wound flushing In breast cancer surgery, warm distilled water is used to flush surgical wounds. This practice helps to clean the wound, remove possible residual tumor cells, and use hypnotic effect to make tumor cells absorb water, swell, rupture, and necrotic, thereby preventing tumors from growing in the wound.
Cleaning and disinfection Distilled water has a certain disinfection and sterilization effect. It can be used to clean the skin, help eliminate bacteria on the skin surface, and is beneficial to the health of the skin. In addition, distilled water can also be used to clean and disinfect medical equipment to ensure the hygiene and safety of the medical environment.
Laboratory use In medical-related laboratories, distilled water is used to prepare experimental solutions, wash utensils and experimental instruments. These applications ensure the accuracy of experimental results while maintaining the sterile environment of the laboratory.
Moisturizing and Beauty Although not directly used in medical applications, distilled water is also used in skin care. It can be used as a basic moisturizer to help improve the symptoms of dry skin. In the field of medical beauty, distilled water is sometimes used for facial compresses to achieve calming, cooling, and swelling effects.
In summary, the application of distilled water in the medical field is multifaceted, from basic injection water preparation to complex surgical assistance to daily skin care, it has played an important role.
-
 @ 9cb3545c:2ff47bca
2025-05-27 12:58:56
@ 9cb3545c:2ff47bca
2025-05-27 12:58:56Introduction
Public companies that hold Bitcoin on behalf of investors (often issuing securities backed by those Bitcoin holdings) have faced growing pressure to demonstrate proof of reserves – evidence that they genuinely hold the cryptocurrency they claim. One approach is to publish the company’s Bitcoin wallet addresses so that anyone can verify the balances on the blockchain. This practice gained momentum after high-profile crypto collapses (e.g. FTX in 2022) eroded trust, leading major exchanges and fund issuers like Binance, Kraken, OKX, and Bitwise to publicize wallet addresses as proof of assets . The goal is transparency and reassurance for investors. However, making wallet addresses public comes with significant security and privacy risks. This report examines those risks – from cybersecurity threats and blockchain tracing to regulatory and reputational implications – and weighs them against the transparency benefits of on-chain proof of reserves.
Proof of Reserves via Public Wallet Addresses
In the cryptocurrency ethos of “don’t trust – verify,” on-chain proof of reserves is seen as a powerful tool. By disclosing wallet addresses (or cryptographic attestations of balances), a company lets investors and analysts independently verify that the Bitcoin reserves exist on-chain. For example, some firms have dashboards showing their addresses and balances in real time . In theory, this transparency builds trust by proving assets are not being misreported or misused. Shareholders gain confidence that the company’s Bitcoin holdings are intact, potentially preventing fraud or mismanagement.
Yet this approach essentially sacrifices the pseudonymity of blockchain transactions. Publishing a wallet address ties a large, known institution to specific on-chain funds. While Bitcoin addresses are public by design, most companies treat their specific addresses as sensitive information. Public proof-of-reserve disclosures break that anonymity, raising several concerns as detailed below.
Cybersecurity Threats from Visible Wallet Balances
Revealing a wallet address with a large balance can make a company a prime target for hackers and cybercriminals. Knowing exactly where significant reserves are held gives attackers a clear blueprint. As Bitcoin advocate (and MicroStrategy Executive Chairman) Michael Saylor warned in 2025, “publicly known wallet addresses become prime targets for malicious actors. Knowing where significant reserves are held provides hackers with a clear target, potentially increasing the risk of sophisticated attacks” . In other words, publishing the address increases the attack surface – attackers might intensify phishing campaigns, malware deployment, or insider bribery aimed at obtaining the keys or access to those wallets.
Even if the wallets are secured in cold storage, a public address advertisement may encourage attempts to penetrate the organization’s security. Custodians and partners could also be targeted. Saylor noted that this exposure isn’t just risky for the company holding the Bitcoin; it can indirectly put their custodial providers and related exchanges at risk as well . For instance, if a third-party custodian manages the wallets, hackers might attempt to breach that custodian knowing the reward (the company’s Bitcoin) is great.
Companies themselves have acknowledged these dangers. Grayscale Investments, which runs the large Grayscale Bitcoin Trust (GBTC), pointedly refused to publish its wallet addresses in late 2022, citing “security concerns” and complex custody arrangements that have “kept our investors’ assets safe for years” . Grayscale implied that revealing on-chain addresses could undermine those security measures, and it chose not to “circumvent complex security arrangements” just to appease public demand . This highlights a key point: corporate treasury security protocols often assume wallet details remain confidential. Publicizing them could invalidate certain assumptions (for example, if an address was meant to be operationally secret, it can no longer serve that role once exposed).
Additionally, a publicly known trove of cryptocurrency might invite physical security threats. While not a purely “cyber” issue, if criminals know a particular company or facility controls a wallet with, say, thousands of Bitcoin, it could lead to threats against personnel (extortion or coercion to obtain keys). This is a less common scenario for large institutions (which typically have robust physical security), but smaller companies or key individuals could face elevated personal risk by being associated with huge visible crypto reserves.
In summary, cybersecurity experts consider public proof-of-reserve addresses a double-edged sword: transparency comes at the cost of advertising exactly where a fortune is held. As Saylor bluntly put it, “the conventional way of issuing proof of reserves today is actually insecure… This method undermines the security of the issuer, the custodian, the exchanges and the investors. This is not a good idea”  . From a pure security standpoint, broadcasting your wallets is akin to drawing a bullseye on them.
Privacy Risks: Address Clustering and Blockchain Tracing
Blockchain data is public, so publishing addresses opens the door to unwanted analytics and loss of privacy for the business. Even without knowing the private keys, analysts can scrutinize every transaction in and out of those addresses. This enables address clustering – linking together addresses that interact – and other forms of blockchain forensics that can reveal sensitive information about the company’s activities.
One immediate risk is that observers can track the company’s transaction patterns. For example, if the company moves Bitcoin from its reserve address to an exchange or to another address, that move is visible in real time. Competitors, investors, or even attackers could deduce strategic information: perhaps the company is planning to sell (if coins go to an exchange wallet) or is reallocating funds. A known institution’s on-chain movements can thus “reveal strategic movements or holdings”, eroding the company’s operational privacy . In a volatile market, advance knowledge of a large buy or sell by a major player could even be exploited by others (front-running the market, etc.).
Publishing one or a few static addresses also violates a basic privacy principle of Bitcoin: address reuse. Best practice in Bitcoin is to use a fresh address for each transaction to avoid linking them  . If a company continuously uses the same “proof of reserve” address, all counterparties sending funds to or receiving funds from that address become visible. Observers could map out the company’s business relationships or vendors by analyzing counterparties. A Reddit user commenting on an ETF that published a single address noted that “reusing a single address for this makes me question their risk management… There are much better and more privacy-preserving ways to prove reserves… without throwing everything in a single public address” . In other words, a naive implementation of proof-of-reserve (one big address) maximizes privacy leakage.
Even if multiple addresses are used, if they are all disclosed, one can perform clustering analysis to find connections. This happened in the Grayscale case: although Grayscale would not confirm any addresses, community analysts traced and identified 432 addresses likely belonging to GBTC’s custodial holdings by following on-chain traces from known intermediary accounts . They managed to attribute roughly 317,705 BTC (about half of GBTC’s holdings) to those addresses . This demonstrates that even partial information can enable clustering – and if the company directly published addresses, the task becomes even easier to map the entirety of its on-chain asset base.
Another threat vector is “dusting” attacks, which become more feasible when an address is publicly known. In a dusting attack, an adversary sends a tiny amount of cryptocurrency (dust) to a target address. The dust itself is harmless, but if the target address ever spends that dust together with other funds, it can cryptographically link the target address to other addresses in the same wallet. Blockchain security researchers note that “with UTXO-based assets, an attacker could distribute dust to an address to reveal the owner’s other addresses by tracking the dust’s movement… If the owner unknowingly combines this dust with their funds in a transaction, the attacker can… link multiple addresses to a single owner”, compromising privacy . A company that publishes a list of reserve addresses could be systematically dusted by malicious actors attempting to map out all addresses under the company’s control. This could unmask cold wallet addresses that the company never intended to publicize, further eroding its privacy and security.
Investor confidentiality is another subtle concern. If the business model involves individual investor accounts or contributions (for instance, a trust where investors can deposit or withdraw Bitcoin), public addresses might expose those movements. An outside observer might not know which investor corresponds to a transaction, but unusual inflows/outflows could signal actions by big clients. In extreme cases, if an investor’s own wallet is known (say a large investor announces their involvement), one might link that to transactions in the company’s reserve addresses. This could inadvertently reveal an investor’s activities or holdings, breaching expectations of confidentiality. Even absent direct identification, some investors might simply be uncomfortable with their transactions being part of a publicly traceable ledger tied to the company.
In summary, publishing reserve addresses facilitates blockchain tracing that can pierce the veil of business privacy. It hands analysts the keys to observe how funds move, potentially exposing operational strategies, counterparties, and internal processes. As one industry publication noted, linking a large known institution to specific addresses can compromise privacy and reveal more than intended . Companies must consider whether they are ready for that level of transparency into their every on-chain move.
Regulatory and Compliance Implications
From a regulatory perspective, wallet address disclosure lies in uncharted territory, but it raises several flags. First and foremost is the issue of incomplete information: A wallet address only shows assets, not the company’s liabilities or other obligations. Regulators worry that touting on-chain holdings could give a false sense of security. The U.S. Securities and Exchange Commission (SEC) has cautioned investors to “not place too much confidence in the mere fact a company says it’s got a proof-of-reserves”, noting that such reports “lack sufficient information” for stakeholders to ascertain if liabilities can be met . In other words, a public company might show a big Bitcoin address balance, but if it has debts or customer liabilities of equal or greater value, the proof-of-reserve alone is “not necessarily an indicator that the company is in a good financial position” .
This regulatory stance implies that address disclosure, if done, must be paired with proper context. A public company would likely need to clarify in its financial statements or investor communications that on-chain reserves are unencumbered (not pledged as loan collateral, not already sold forward, etc.) and that total liabilities are accounted for. Otherwise, there’s a risk of misleading investors, which could have legal consequences. For example, if investors interpret the on-chain balance as proof of solvency but the company actually had leveraged those bitcoins for loans, lawsuits or regulatory enforcement could follow for misrepresentation.
There’s also a compliance burden associated with revealing addresses. Once an address is known to be the company’s, that company effectively must monitor all transactions related to it. If someone sends funds to that address (even without permission), the company might receive tainted coins (from hacked sources or sanctioned entities). This could trigger anti-money laundering (AML) red flags. Normally, compliance teams can ignore random deposits to unknown wallets, but they cannot ignore something sent into their publicly identified corporate wallet. Even a tiny dust amount sent from a blacklisted address could complicate compliance – for instance, the company would need to prove it has no relation to the sender and perhaps even avoid moving those tainted outputs. Being in the open increases such exposure. Threat actors might even exploit this by “poisoning” a company’s address with unwanted transactions, just to create regulatory headaches or reputational smears.
Another consideration is that custodial agreements and internal risk controls might forbid public disclosure of addresses. Many public companies use third-party custodians for their Bitcoin (for example, Coinbase Custody, BitGo, etc.). These custodians often treat wallet details as confidential for security. Grayscale noted that its Bitcoin are custodied on Coinbase and implied that revealing on-chain info would interfere with security arrangements  . It’s possible that some custodians would object to their clients broadcasting addresses, or might require additional assurances. A company going against such advice might be seen as negligent if something went wrong.
Regulators have so far not mandated on-chain proofs for public companies – in fact, recent laws have exempted public companies from proof-of-reserve mandates on the assumption they are already subject to rigorous SEC reporting. For example, a Texas bill in 2023 required crypto exchanges and custodians to provide quarterly proof-of-reserves to the state, but it “specifically carved out public reporting companies” since they already file audited financials with the SEC . The rationale was that between SEC filings and audits, public companies have oversight that private crypto firms lack . However, this also highlights a gap: even audited financials might not verify 100% of crypto assets (auditors often sample balances). Some observers noted that standard audits “may not ever include the 100% custodial asset testing contemplated by proof of reserves”, especially since quarterly SEC filings (10-Q) are often not audited . This puts public companies in a nuanced position – they are trusted to use traditional audits and internal controls, but the onus is on them if they choose to add extra transparency like on-chain proofs.
Finally, securities regulators focus on fair disclosure and accuracy. If a company publicly posts addresses, those essentially become investor disclosures subject to anti-fraud rules. The firm must keep them up to date and accurate. Any mistake (such as publishing a wrong address or failing to mention that some coins are locked up or lent out) could attract regulatory scrutiny for being misleading. In contrast, a formal audit or certification from a third-party comes with standards and disclaimers that are better understood by regulators. A self-published wallet list is an unprecedented form of disclosure that regulators haven’t fully vetted – meaning the company bears the risk if something is misinterpreted.
In summary, wallet address disclosure as proof-of-reserve must be handled very carefully to avoid regulatory pitfalls. The SEC and others have warned that on-chain assets alone don’t tell the whole story . Public companies would need to integrate such proofs with their official reporting in a responsible way – otherwise they risk confusion or even regulatory backlash for giving a false sense of security.
Reputational and Operational Risks
While transparency is meant to enhance reputation, in practice public wallet disclosures can create new reputational vulnerabilities. Once an address is public, a company’s every on-chain action is under the microscope of the crypto community and media. Any anomaly or perceived misstep can snowball into public relations problems.
One vivid example occurred with Crypto.com in late 2022. After the exchange published its cold wallet addresses to prove reserves (a move prompted by the FTX collapse), on-chain analysts quickly noticed a “suspicious transfer of 320,000 ETH” – about 82% of Crypto.com’s Ether reserves – moving from their cold wallet to another exchange (Gate.io)  . This large, unexpected transfer sparked immediate panic and FUD (fear, uncertainty, and doubt) on social media. Observers speculated that Crypto.com might be insolvent or was manipulating snapshots of reserves by borrowing funds. The CEO had to publicly respond, admitting it was an operational error – the ETH was supposed to go to a new cold storage address but ended up at a whitelisted external address by mistake . The funds were eventually returned, but not before reputational damage was done: the incident made headlines about mishandled funds and rattled user confidence  . This case illustrates how full public visibility can turn an internal slip-up into a highly public crisis. If the addresses had not been public, the mistake might have been quietly corrected; with on-chain transparency, there was nowhere to hide and no way to control the narrative before the public drew worst-case conclusions.
Even routine operations can be misinterpreted. Blockchain data lacks context – analysts may jump to conclusions that hurt a company’s reputation even if nothing is actually wrong. For instance, Binance (the world’s largest crypto exchange) encountered scrutiny when on-chain observers noted that one of its reserve wallets (labeled “Binance 8”) contained far more assets than it should have. This wallet was meant to hold collateral for Binance’s issued tokens, but held an excess balance, suggesting possible commingling of customer funds with collateral  . Bloomberg and others reported a ~$12.7 billion discrepancy visible on-chain . Binance had to acknowledge the issue as a “clerical error” and quickly separate the funds, all under the glare of public attention  . While Binance maintained that user assets were fully backed and the mistake was purely operational, the episode raised public concern over Binance’s practices, feeding a narrative that even the largest exchange had internal control lapses. The key point is that public proof-of-reserves made the lapse obvious to everyone, forcing a reactive explanation. The reputational hit (even if temporary) was an operational risk of being so transparent.
Additionally, strategic confidentiality is lost. If a company holding Bitcoin as a reserve asset decides to make a major move (say, reallocating to a different wallet, or using some Bitcoin for a strategic investment or loan), doing so with known addresses broadcasts that strategy. Competitors or market analysts can infer things like “Company X is moving 10% of its BTC — why? Are they selling? Hedging? Using it as collateral?” This can erode any competitive advantage of keeping financial strategies discreet. It might even affect the company’s stock price if investors interpret moves negatively. For example, if a blockchain analysis shows the company’s reserves dropping, shareholders might fear the company sold Bitcoin (perhaps due to financial distress), even if the reality is benign (like moving funds to a new custodian). The company would be forced into continuous public explanation of on-chain actions to prevent misunderstanding.
There’s also a risk of exposing business partnerships. Suppose the company uses certain exchanges or OTC desks to rebalance its holdings – transactions with those service providers will be visible and could link the company to them. If one of those partners has issues (say a hacked exchange or a sanctioned entity inadvertently), the company could be reputationally contaminated by association through the blockchain trail.
Finally, not all publicity is good publicity in the crypto world. A public proof-of-reserve might invite armchair auditors to scrutinize and criticize every aspect of the company’s crypto management. Minor issues could be blown out of proportion. On the flip side, if a company chooses not to publish addresses, it could face reputational risk from a different angle: skeptics might question why it isn’t being transparent. (Indeed, Grayscale’s refusal to disclose wallet addresses led to social media chatter about whether they truly held all the Bitcoin they claimed, contributing to investor nervousness and a steep discount on GBTC shares .) Thus, companies are in a delicate spot: share too much and every move invites scrutiny; share too little and you breed distrust.
Balancing Transparency Benefits vs. Risks
The central question is whether the benefit of proving reserve holdings to investors outweighs these security and privacy risks. It’s a classic risk-reward calculation, and opinions in the industry are divided.
On the side of transparency, many argue that the credibility and trust gained by proof-of-reserves is invaluable. Advocates note that Bitcoin was designed for open verification – “on-chain auditability and permissionless transparency” are core features . By embracing this, companies demonstrate they are good stewards of a “trustless” asset. In fact, some believe public companies have a duty to be extra transparent. A recent Nasdaq report contended that “when a publicly traded company holds Bitcoin but offers no visibility into how that Bitcoin is held or verified, it exposes itself to multiple levels of risk: legal, reputational, operational, and strategic”, undermining trust . In that view, opacity is riskier in the long run – a lack of proof could weaken investor confidence or invite regulatory suspicion. Shareholders and analysts may actually penalize a company that refuses to provide verifiable proof of its crypto assets .
Transparency done right can also differentiate a firm as a leader in governance. Publishing reserve data (whether via addresses or through third-party attestations) can be seen as a commitment to high standards. For example, Metaplanet, an investment firm, publicly discloses its BTC reserve addresses and even provides a live dashboard for anyone to verify balances . This proactive openness signals confidence and has been touted as an industry best practice in some quarters. By proving its reserves, a company can potentially avoid the fate of those that lost public trust (as happened with opaque crypto firms in 2022). It’s also a means to preempt false rumors – if data is out in the open, misinformation has less room to grow.
However, the pro-transparency camp increasingly acknowledges that there are smarter ways to achieve trust without courting all the risks. One compromise is using cryptographic proofs or audits instead of plain address dumps. For instance, exchanges like Kraken have implemented Merkle tree proof-of-reserves: an independent auditor verifies all customer balances on-chain and provides a cryptographic report, and customers can individually verify their account is included without the exchange revealing every address publicly. This method proves solvency to those who need to know without handing over a complete roadmap to attackers. Another emerging solution is zero-knowledge proofs, where a company can prove knowledge or ownership of certain assets without revealing the addresses or amounts to the public. These technologies are still maturing, but they aim to deliver the best of both worlds: transparency and privacy.
On the side of caution, many experts believe the risks of full public disclosure outweigh the incremental gain in transparency, especially for regulated public companies. Michael Saylor encapsulates this viewpoint: he calls on-chain proof-of-reserve “a bad idea” for institutions, arguing that it “offers one-way transparency” (assets only) and “leaves organizations open to cyberattacks” . He stresses that no serious security expert would advise a Fortune 500 company to list all its wallet addresses, as it essentially compromises corporate security over time . Saylor and others also point out the pointlessness of an assets-only proof: unless you also prove liabilities, showing off reserves might even be dangerous because it could lull investors into a false sense of security .
Regulators and traditional auditors echo this: proof-of-reserves, while a useful tool, “is not enough by itself” to guarantee financial health . They advocate for holistic transparency – audits that consider internal controls, liabilities, and legal obligations, not just a snapshot of a blockchain address  . From this perspective, a public company can satisfy transparency demands through rigorous third-party audits and disclosures rather than raw on-chain data. Indeed, public companies are legally bound to extensive reporting; adding public crypto addresses on top may be seen as redundant and risky.
There is also an implicit cost-benefit analysis: A successful attack resulting from over-sharing could be catastrophic (loss of funds, legal liability, reputational ruin), whereas the benefit of public proof is somewhat intangible (improved investor sentiment, which might be achieved via other assurance methods anyway). Given that trade-off, many firms err on the side of caution. As evidence, few if any U.S.-listed companies that hold Bitcoin have published their wallet addresses. Instead, they reference independent custodians and audits for assurance. Even crypto-native companies have pulled back on full transparency after realizing the downsides – for example, some auditing firms halted issuing proof-of-reserves reports due to concerns about how they were interpreted and the liability involved  .
Industry best practices are still evolving. A prudent approach gaining favor is to prove reserves without leaking sensitive details. This can involve disclosing total balances and having an auditor or blockchain oracle confirm the assets exist, but without listing every address publicly. Companies are also encouraged to disclose encumbrances (whether any of the reserves are collateralized or lent out) in tandem, to address the liabilities issue . By doing so, they aim to achieve transparency and maintain security.
In evaluating whether to publish wallet addresses, a company must ask: Will this level of openness meaningfully increase stakeholder trust, or would a more controlled disclosure achieve the same goal with less risk? For many public companies, the answer has been to avoid public addresses. The risks – from attracting hackers to revealing strategic moves – tend to outweigh the marginal transparency benefit in their judgment. The collapse of unregulated exchanges has certainly proven the value of reserve verification, but public companies operate in a different context with audits and legal accountability. Thus, the optimal solution may be a middle ground: proving reserves through vetted processes (auditor attestations, cryptographic proofs) that satisfy investor needs without blatantly exposing the company’s financial backend to the world.
Conclusion
Publishing Bitcoin wallet addresses as proof of reserves is a bold transparency measure – one that speaks to crypto’s ideals of open verification – but it comes with a laundry list of security considerations. Public companies weighing this approach must contend with the heightened cybersecurity threat of advertising their treasure troves to hackers, the loss of privacy and confidentiality as on-chain sleuths dissect their every transaction, and potential regulatory complications if such disclosures are misunderstood or incomplete. Real-world incidents illustrate the downsides: firms that revealed addresses have seen how quickly online communities flag (and sometimes misinterpret) their blockchain moves, causing reputational turbulence and forcing rapid damage control  .
On the other hand, proving reserves to investors is important – it can prevent fraud and bolster trust. The question is how to achieve it without incurring unacceptable risk. Many experts and industry leaders lean towards the view that simply publishing wallet addresses is too risky a method, especially for public companies with much to lose  . The risks often do outweigh the direct benefits in such cases. Transparency remains crucial, but it can be provided in safer ways – through regular audits, cryptographic proofs that don’t expose all wallet details, and comprehensive disclosures that include liabilities and controls.
In conclusion, while on-chain proof of reserves via public addresses offers a tantalizing level of openness, it must be approached with extreme caution. For most public companies, the smart strategy is to balance transparency with security: verify and show investors that assets exist and are sufficient, but do so in a controlled manner that doesn’t compromise the very assets you’re trying to protect. As the industry matures, we can expect more refined proof-of-reserve practices that satisfy the demand for honesty and solvency verification without unduly endangering the enterprise. Until then, companies will continue to tread carefully, mindful that transparency is only truly valuable when it doesn’t come at the price of security and trust.
Sources:
• Grayscale statement on refusal to share on-chain proof-of-reserves  • Community analysis identifying Grayscale’s wallet addresses  • Cointelegraph – Crypto.com’s mistaken 320k ETH transfer spotted via on-chain proof-of-reserves   • Axios – Binance wallet “commingling” error observed on-chain   • Michael Saylor’s remarks on security risks of publishing wallet addresses    • SEC Acting Chief Accountant on limitations of proof-of-reserves reports  • Nasdaq (Bitcoin for Corporations) – argument for corporate transparency & proof-of-reserves    • 1inch Security Blog – explanation of dusting attacks and privacy loss via address linking  -
 @ eb0157af:77ab6c55
2025-05-28 07:01:26
@ eb0157af:77ab6c55
2025-05-28 07:01:26Governor Abbott will have to decide whether to sign the bill establishing a bitcoin reserve for the state.
Texas could become the third U.S. state to set up a strategic bitcoin reserve, following the approval of Senate Bill 21 by the state House, with 101 votes in favor and 42 against.
Lee Bratcher, founder and president of the Texas Blockchain Council, expressed confidence that Governor Greg Abbott will sign the legislative measure. In an interview with The Block, Bratcher said:
“I’ve talked to the governor about this personally, and I think he wants to see Texas lead in this way.”
The bill is expected to reach the governor’s desk within a week or two, according to Bratcher’s projections. If signed, Texas would follow in the footsteps of New Hampshire and Arizona in creating a state-held bitcoin reserve.
Despite Texas ranking as the world’s eighth-largest economy — ahead of many nations — the initial approach to the reserve will be cautious. Bratcher estimates the starting investment will be in the “tens of millions of dollars,” an amount he describes as “modest” for an economy the size of Texas. The responsibility for operational decisions would fall to the state comptroller, who acts as an executive accountant in charge of managing and investing public funds.
“My sense is that it will be in the tens of millions of dollars, which, while it sounds significant, is a very modest amount, for a state the size of Texas.” explained the president of the Texas Blockchain Council.
The road to approval
According to Bratcher, the idea of creating a state bitcoin reserve dates back to 2022 and represents the culmination of years of work by the Texas Blockchain Council. The organization has worked closely with lawmakers who shared the vision of seeing the state accumulate the world’s leading cryptocurrency. Additionally, Texas has long been home to numerous bitcoin mining companies.
The post Texas one step away from a bitcoin reserve: only the governor’s signature is missing appeared first on Atlas21.
-
 @ 90c656ff:9383fd4e
2025-05-27 11:27:26
@ 90c656ff:9383fd4e
2025-05-27 11:27:26Since its creation, Bitcoin has been a revolutionary asset, challenging the traditional financial system and proposing a new form of decentralized money. However, its future remains uncertain and the subject of intense debate. Among the possible outcomes, two extreme scenarios stand out: hyperbitcoinization-where Bitcoin becomes the dominant currency in the global economy—and obsolescence, where the network loses relevance and is replaced by other solutions.
- Hyperbitcoinization: The World Adopts Bitcoin as a Monetary Standard
01 - Loss of trust in fiat currencies: Due to excessive money printing by central banks, many economies face rampant inflation. Bitcoin, with its fixed supply of 21 million units, emerges as a more trustworthy alternative.
02 - Growing adoption by companies and governments: Some countries have already begun integrating Bitcoin into their economies, accepting it for payments and as a store of value. If this trend continues, Bitcoin’s legitimacy as a global currency will grow.
03 - Ease of global transactions: Bitcoin enables fast and low-cost international transfers, removing the need for financial intermediaries and reducing operational costs.
04 - Technological advancements: Scalability improvements, such as the Lightning Network, can make Bitcoin more efficient for daily use, encouraging mass adoption.
If hyperbitcoinization becomes reality, the world may witness a radical shift in the financial system—with greater decentralization, censorship resistance, and an economy based on sound, predictable money.
- Obsolescence: Bitcoin Loses Relevance and Is Replaced
01 - Restrictive government regulations: If major economic powers enforce strict regulations on Bitcoin, adoption could slow, reducing its utility.
02 - Technological shortcomings or lack of innovation: Despite its security and decentralization, Bitcoin may struggle to scale effectively. If superior solutions emerge and gain acceptance, Bitcoin could lose its leading position.
03 - Competition from faster, more user-friendly alternatives: Other forms of digital money may surpass Bitcoin in scalability and usability, potentially leading to a decline in Bitcoin adoption.
04 - Decreasing miner incentives: As new Bitcoin issuance halves every four years, miners will rely increasingly on transaction fees. If those fees are insufficient to sustain network security, long-term viability could be at risk.
In summary, Bitcoin’s future could unfold along multiple paths, depending on factors like innovation, global adoption, and resilience to external challenges. Hyperbitcoinization would represent an economic revolution—ushering in a decentralized, inflation-resistant monetary system. Yet, obsolescence remains a risk if the network fails to adapt to future demands. Regardless of the outcome, Bitcoin has already made its mark on financial history, paving the way for a new era of digital money and economic freedom.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ 90c656ff:9383fd4e
2025-05-27 11:22:10
@ 90c656ff:9383fd4e
2025-05-27 11:22:10Since its creation, Bitcoin has been much more than just an alternative to traditional money. With the ongoing digitalization of the global economy, Bitcoin has emerged as a foundational pillar for new forms of transactions, commerce, and value storage. Its decentralization, transparency, and censorship resistance make it a solid base for digital economies, where financial interactions occur without the need for traditional intermediaries.
- Bitcoin’s role in the digital economy
01 - Global, borderless transactions: Anyone with internet access can send and receive Bitcoin without needing a bank or government authorization.
02 - Limited and predictable supply: Unlike fiat currencies that can be inflated by central banks, Bitcoin has a fixed cap of 21 million units, making it a scarce and reliable asset.
03 - Security and transparency: The Bitcoin blockchain or timechain publicly records all transactions, ensuring a secure and auditable system.
04 - Censorship resistance: No government or institution can block Bitcoin transactions, enabling a freer and more accessible digital economy.
With these characteristics, Bitcoin is already transforming various economic sectors and driving new forms of commerce and investment.
- Bitcoin in digital commerce and the global economy
01 - E-commerce: Businesses and consumers can use Bitcoin for fast international transactions without exorbitant fees.
02 - International remittances: Workers sending money to their home countries can avoid high fees and long delays by using Bitcoin.
03 - Emerging economies: In countries with unstable currencies and unreliable banking systems, Bitcoin serves as a secure and decentralized alternative for storing wealth and conducting daily transactions.
Additionally, Bitcoin is being adopted by companies and even governments as a store of value, reinforcing its role as a foundation for the digital economy of the future.
- Challenges and adapting to the new economy
01 - Price volatility: Bitcoin’s fluctuating value can make it difficult to use as a daily medium of exchange.
02 - Regulations and governmental resistance: Some countries attempt to restrict or regulate Bitcoin to maintain control over the traditional financial system.
03 - Education and adoption: Many people still lack the knowledge to use Bitcoin safely and effectively.
In summary, Bitcoin is transforming the way the world interacts with money, offering a decentralized and transparent alternative for digital economies. As more individuals and businesses adopt Bitcoin for payments, savings, and global commerce, its impact becomes increasingly clear. Despite the challenges, Bitcoin continues to solidify its place as the foundation of a new economic paradigm—where financial freedom and technological innovation go hand in hand.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ eb0157af:77ab6c55
2025-05-28 07:01:26
@ eb0157af:77ab6c55
2025-05-28 07:01:26Bitcoin surpasses gold in the United States: 50 million holders and a dominant role in the global market.
According to a new report by River, for the first time in history, the number of Americans owning bitcoin has surpassed that of gold holders. The analysis reveals that approximately 50 million U.S. citizens currently own the cryptocurrency, while gold owners number 37 million. In fact, 14.3% of Americans own bitcoin, the highest percentage of holders worldwide.

Source: River
The report highlights that 40% of all Bitcoin-focused companies are based in the United States, consolidating America’s dominant position in the sector. Additionally, 40.5% of Bitcoin holders are men aged 31 to 35, followed by 35.9% of men aged 41 to 45. In contrast, only 13.4% of holders are women.

Source: River
Notably, U.S. companies hold 94.8% of all bitcoins owned by publicly traded companies worldwide. According to the report, recent regulatory changes in the U.S. have made the asset more accessible through financial products such as spot ETFs.
The document also shows that American investors increasingly view the cryptocurrency as protection against fiscal instability and inflation, appreciating its limited supply and decentralized governance model.
For River, Bitcoin offers significant practical advantages over gold in the modern digital era. Its ease of custody, cross-border transfer, and liquidity make the cryptocurrency an attractive option for both individual and institutional investors, the report suggests.
The post USA: 50 million Americans own bitcoin appeared first on Atlas21.
-
 @ 866e0139:6a9334e5
2025-05-27 10:15:17
@ 866e0139:6a9334e5
2025-05-27 10:15:17Autor: Milosz Matuschek. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie auch in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Der Schweizer Historiker Daniele Ganser startet eine Plakataktion. Auf Facebook schreibt er:
"Dieses Plakat habe ich ab heute an sechs Bahnhöfen in der Schweiz aufhängen lassen: Die Schweiz muss die Neutralität bewahren. Keine Zusammenarbeit mit der NATO!
Die Aktion läuft eine Woche. Das Plakat hängt in Basel (Gleis 5 und 7), Zürich (Gleis 9 und 12), Bern (Gleis 3 und 11), Luzern (Gleis 7 und 11), St. Gallen (Gleis 1 und 2) und Chur (Gleis 4 und Arosabahn).
Wenn jemand ein Plakat sieht und fotografiert und es mir per Email schickt freut mich das!
https://globalbridge.ch/die-schweiz-muss-die.../
Daniele Ganser kann man über folgende Seite kontaktieren.
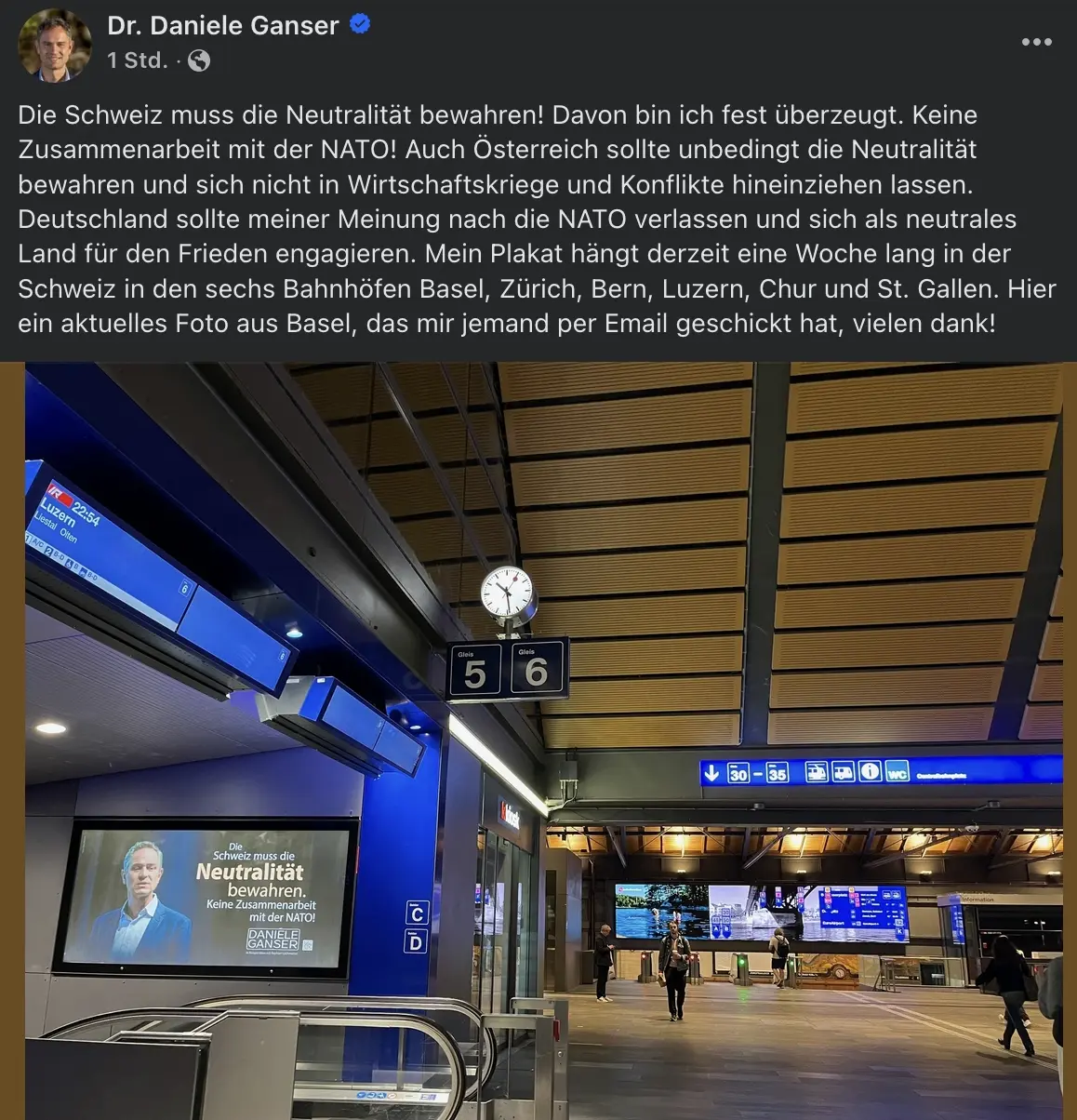
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 39cc53c9:27168656
2025-05-27 09:21:53
@ 39cc53c9:27168656
2025-05-27 09:21:53The new website is finally live! I put in a lot of hard work over the past months on it. I'm proud to say that it's out now and it looks pretty cool, at least to me!
Why rewrite it all?
The old kycnot.me site was built using Python with Flask about two years ago. Since then, I've gained a lot more experience with Golang and coding in general. Trying to update that old codebase, which had a lot of design flaws, would have been a bad idea. It would have been like building on an unstable foundation.
That's why I made the decision to rewrite the entire application. Initially, I chose to use SvelteKit with JavaScript. I did manage to create a stable site that looked similar to the new one, but it required Jav aScript to work. As I kept coding, I started feeling like I was repeating "the Python mistake". I was writing the app in a language I wasn't very familiar with (just like when I was learning Python at that mom ent), and I wasn't happy with the code. It felt like spaghetti code all the time.
So, I made a complete U-turn and started over, this time using Golang. While I'm not as proficient in Golang as I am in Python now, I find it to be a very enjoyable language to code with. Most aof my recent pr ojects have been written in Golang, and I'm getting the hang of it. I tried to make the best decisions I could and structure the code as well as possible. Of course, there's still room for improvement, which I'll address in future updates.
Now I have a more maintainable website that can scale much better. It uses a real database instead of a JSON file like the old site, and I can add many more features. Since I chose to go with Golang, I mad e the "tradeoff" of not using JavaScript at all, so all the rendering load falls on the server. But I believe it's a tradeoff that's worth it.
What's new
- UI/UX - I've designed a new logo and color palette for kycnot.me. I think it looks pretty cool and cypherpunk. I am not a graphic designer, but I think I did a decent work and I put a lot of thinking on it to make it pleasant!
- Point system - The new point system provides more detailed information about the listings, and can be expanded to cover additional features across all services. Anyone can request a new point!
- ToS Scrapper: I've implemented a powerful automated terms-of-service scrapper that collects all the ToS pages from the listings. It saves you from the hassle of reading the ToS by listing the lines that are suspiciously related to KYC/AML practices. This is still in development and it will improve for sure, but it works pretty fine right now!
- Search bar - The new search bar allows you to easily filter services. It performs a full-text search on the Title, Description, Category, and Tags of all the services. Looking for VPN services? Just search for "vpn"!
- Transparency - To be more transparent, all discussions about services now take place publicly on GitLab. I won't be answering any e-mails (an auto-reply will prompt to write to the corresponding Gitlab issue). This ensures that all service-related matters are publicly accessible and recorded. Additionally, there's a real-time audits page that displays database changes.
- Listing Requests - I have upgraded the request system. The new form allows you to directly request services or points without any extra steps. In the future, I plan to enable requests for specific changes to parts of the website.
- Lightweight and fast - The new site is lighter and faster than its predecessor!
- Tor and I2P - At last! kycnot.me is now officially on Tor and I2P!
How?
This rewrite has been a labor of love, in the end, I've been working on this for more than 3 months now. I don't have a team, so I work by myself on my free time, but I find great joy in helping people on their private journey with cryptocurrencies. Making it easier for individuals to use cryptocurrencies without KYC is a goal I am proud of!
If you appreciate my work, you can support me through the methods listed here. Alternatively, feel free to send me an email with a kind message!
Technical details
All the code is written in Golang, the website makes use of the chi router for the routing part. I also make use of BigCache for caching database requests. There is 0 JavaScript, so all the rendering load falls on the server, this means it needed to be efficient enough to not drawn with a few users since the old site was reporting about 2M requests per month on average (note that this are not unique users).
The database is running with mariadb, using gorm as the ORM. This is more than enough for this project. I started working with an
sqlitedatabase, but I ended up migrating to mariadb since it works better with JSON.The scraper is using chromedp combined with a series of keywords, regex and other logic. It runs every 24h and scraps all the services. You can find the scraper code here.
The frontend is written using Golang Templates for the HTML, and TailwindCSS plus DaisyUI for the CSS classes framework. I also use some plain CSS, but it's minimal.
The requests forms is the only part of the project that requires JavaScript to be enabled. It is needed for parsing some from fields that are a bit complex and for the "captcha", which is a simple Proof of Work that runs on your browser, destinated to avoid spam. For this, I use mCaptcha.
-
 @ 39cc53c9:27168656
2025-05-27 09:21:51
@ 39cc53c9:27168656
2025-05-27 09:21:51Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations.
Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms.
Rights for Illusions
KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks?
The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors."
However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% ^1 – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service.
Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy.
To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% ^1 of less-than-careful criminals.
KYC? Not you.
KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. ^2
KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible.
For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded.
Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether.
It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms.
You're not welcome
Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right?
This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to.
Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely.
Your identity has been stolen
KYC data has been found to be for sale on many dark net markets^3. Exchanges may have leaks or hacks, and such leaks contain very sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it?
As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. ^3
In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised.
(they) Know Your Coins
You may already know that Bitcoin and most cryptocurrencies have a transparent public blockchain, meaning that all data is shown unencrypted for everyone to see and recorded forever. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced.
If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with.
Conclusions
To sum up, KYC does not protect individuals; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred.
The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies.
The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable.
Edited 20/03/2024 * Add reference to the 1% statement on Rights for Illusions section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity ^1
-
 @ 9c9d2765:16f8c2c2
2025-05-28 05:42:53
@ 9c9d2765:16f8c2c2
2025-05-28 05:42:53CHAPTER THIRTY ONE
One quiet evening, as the golden hues of sunset spilled across the office, James found himself standing by the door of Rita’s private workspace. He knocked gently.
She looked up, startled but composed. “James,” she said softly, setting her pen down.
“May I?” he asked, motioning to the chair across from her desk.
She nodded, her expression unreadable. “Of course.”
There was a brief silence, heavy but not uncomfortable. Then James leaned forward, his voice low and sincere.
“Rita… I never hated you,” he began. “Not even for a moment.”
Her eyes flickered, and she looked away, blinking fast. “You should have,” she replied. “I believed lies, I stood by while they treated you like nothing. I was” her voice cracked, “I was a coward.”
“No,” James shook his head. “You were misled. Just like I was, at one point, about the people I trusted.”
He paused, choosing his words carefully. “But everything I did building JP back from ruins, exposing the ones who tried to destroy us, it was never about revenge. It was about finding the truth, and… hoping that maybe, there was still something worth saving between us.”
Tears welled in her eyes, and for the first time in a long time, she didn’t hide them. “Do you really believe we can go back to what we had?”
James offered a small, tender smile. “No. But maybe we can build something new. Something stronger this time with no secrets, no walls.”
That night marked a shift. Rita and James didn’t rush back into love, but they started anew with honesty. Slowly, they began to reconnect over coffee breaks, shared boardroom victories, and late-night reflections.
Meanwhile, the city’s perception of James continued to evolve. He became a keynote speaker at leadership summits, not for his wealth, but for his story. His life, once the subject of cruel gossip, became a testament to resilience, clarity, and vision.
Even the youngest interns in JP Enterprises admired him, not just as a CEO, but as a symbol of what it meant to stand upright in a world eager to bring you down.
Back in the shadows, Mark and Helen's trial proceeded. Witnesses testified, evidence was overwhelming, and public opinion had fully turned against them. Their fall from grace was not swift but it was absolute.
One morning, as James read the headlines declaring Mark and Helen guilty on multiple charges, he simply folded the paper and sipped his tea. There was no celebration. No smirk of triumph.
Only peace.
“Do you still think about the past?” Rita’s voice was soft, almost swallowed by the crackling of the fireplace in the private lounge of JP Towers.
James, seated across from her with a warm mug in his hand, raised his eyes to meet hers. The flicker of flames cast shadows on the polished walls, painting a solemn reflection of everything they'd endured.
“I do,” he admitted, his tone neither bitter nor nostalgic. “Not because I want to relive it but because it reminds me how far we’ve come. How far I’ve come.”
Rita nodded slowly, her eyes glistening beneath the soft glow. “I think about it too,” she confessed. “Every time I walk past the corridors, or sit at my desk… I remember the days I watched you walk these halls like a ghost. Silenced. Humiliated. And I did nothing.”
James leaned back slightly, inhaling deeply. “You did what you thought was right then,” he said with a hint of melancholy. “We were both just trying to survive the storm.”
There was a long pause. Outside, the city pulsed with its usual life, unaware of the quiet reconciliation happening several floors above.
“But survival isn’t living,” she said at last, her voice steadier now. “And I want to live, James. I want to find joy again… with you, if you'll let me.”
Her words hung in the air like fragile glass. James was silent, studying her. This wasn’t the composed, dutiful woman who once echoed the will of her family. This was someone stripped of expectations, speaking from a place of sincerity.
“I won’t promise perfection,” James said after a beat. “But I’ll promise honesty. Loyalty. Peace. No masks. No power games. Just us healing, rebuilding, slowly.”
She exhaled in relief, the corners of her lips lifting slightly. “Then let’s take the first step.”
They stood, a little uncertain, but walked side by side to the balcony overlooking the city that once spat on him, that now bowed to his vision. Rita slipped her hand into his, and this time, James didn’t pull away.
Meanwhile…
The consequences of Mark and Helen’s conspiracy deepened. Investigative journalists began digging further into their past activities, frauds, embezzlements, manipulations. Their names were now synonymous with disgrace in the business world.
The court trials were intense. Mark, once smug and untouchable, appeared gaunt, stripped of the charisma that used to command a room. Helen, on the other hand, wore arrogance like a decaying crown still trying to act superior even when the evidence against her mounted beyond redemption.
And in every newspaper, every media report, James's name was cleared. He had not only reclaimed his honor but redefined what it meant to rise from ruin.
JP Enterprises, now entering its new era of innovation and social impact, had become more than just a corporation it had become a beacon. Business leaders from around the world sought James’s insight. Young entrepreneurs quoted him in lectures and motivational events. And amidst all this, James remained centered because his heart no longer ached with resentment.
The courtroom was saturated with an electrifying silence. The once-glorious reputations of Mark and Helen now hung like withered banners in the wind tattered by deceit, dishonor, and damning evidence. As the judge stepped into the chamber, all eyes turned, yet Mark’s once-confident gaze had diminished into a hollow stare. Helen, dressed in muted tones as if mourning her own prestige, sat rigidly beside him, still refusing to acknowledge the gravity of their downfall.
“For crimes including corporate fraud, defamation, bribery, and obstruction of justice,” the judge’s voice echoed through the courtroom, “this court finds the defendants, Mark Harrison and Helen Ray, guilty on all counts.”
-
 @ 39cc53c9:27168656
2025-05-27 09:21:50
@ 39cc53c9:27168656
2025-05-27 09:21:50Over the past few months, I've dedicated my time to a complete rewrite of the kycnot.me website. The technology stack remains unchanged; Golang paired with TailwindCSS. However, I've made some design choices in this iteration that I believe significantly enhance the site. Particularly to backend code.
UI Improvements
You'll notice a refreshed UI that retains the original concept but has some notable enhancements. The service list view is now more visually engaging, it displays additional information in a more aesthetically pleasing manner. Both filtering and searching functionalities have been optimized for speed and user experience.
Service pages have been also redesigned to highlight key information at the top, with the KYC Level box always accessible. The display of service attributes is now more visually intuitive.
The request form, especially the Captcha, has undergone substantial improvements. The new self-made Captcha is robust, addressing the reliability issues encountered with the previous version.
Terms of Service Summarizer
A significant upgrade is the Terms of Service summarizer/reviewer, now powered by AI (GPT-4-turbo). It efficiently condenses each service's ToS, extracting and presenting critical points, including any warnings. Summaries are updated monthly, processing over 40 ToS pages via the OpenAI API using a self-crafted and thoroughly tested prompt.
Nostr Comments
I've integrated a comment section for each service using Nostr. For guidance on using this feature, visit the dedicated how-to page.
Database
The backend database has transitioned to pocketbase, an open-source Golang backend that has been a pleasure to work with. I maintain an updated fork of the Golang SDK for pocketbase at pluja/pocketbase.
Scoring
The scoring algorithm has also been refined to be more fair. Despite I had considered its removal due to the complexity it adds (it is very difficult to design a fair scoring system), some users highlighted its value, so I kept it. The updated algorithm is available open source.
Listings
Each listing has been re-evaluated, and the ones that were no longer operational were removed. New additions are included, and the backlog of pending services will be addressed progressively, since I still have access to the old database.
API
The API now offers more comprehensive data. For more details, check here.
About Page
The About page has been restructured for brevity and clarity.
Other Changes
Extensive changes have been implemented in the server-side logic, since the whole code base was re-written from the ground up. I may discuss these in a future post, but for now, I consider the current version to be just a bit beyond beta, and additional updates are planned in the coming weeks.
-
 @ 9c9d2765:16f8c2c2
2025-05-28 05:22:33
@ 9c9d2765:16f8c2c2
2025-05-28 05:22:33In a quiet village nestled between forest and field, lived a boy named Ezekiel. From birth, he was surrounded by a warm family, playful siblings, and neighbors who always had a story to share. Ezekiel never knew silence, and because of that, he never valued voices. To him, connection was like air everywhere, constant, and unnoticed.
One summer, Ezekiel decided to explore the woods beyond the hills, chasing the thrill of adventure. He wandered farther than he ever had, until the trees thickened and the path thinned into nothing. A sudden storm rolled in. Rain blurred the forest, and Ezekiel lost his way. He sought shelter in a small, abandoned stone hut beside a dried-up well.
The storm passed, but no path appeared. Days turned to weeks. His voice echoed off the stone, unanswered. The silence was no longer peaceful; it was heavy, like a weight pressing on his soul. He learned to survive on roots and rainwater. But loneliness is true, aching loneliness clung to him. He spoke to the walls, to the trees, to the echo in the well, but nothing replied.
One day, while resting against the well, Ezekiel whispered, “I miss them.”
And for the first time, he meant it.
Not just missed their presence but their interruptions, their noise, even their complaints. He missed being seen, and seeing. He understood now: connection wasn’t just comfort. It was color, depth, meaning.
Weeks later, a group of searchers found him thin, dirty, but alive. When he returned, everything was the same, but Ezekiel was not.
He listened differently. Hugged longer. Remembered people’s names, stories, and silences. He no longer saw connection as a given, but a gift.
And every year, he visited the well not to mourn the solitude, but to thank it. For in its quiet, he learned the true value of every voice he once ignored.
Moral: To cherish connection, you must understand solitude not as punishment, but as teacher.
-
 @ 39cc53c9:27168656
2025-05-27 09:21:48
@ 39cc53c9:27168656
2025-05-27 09:21:48I'm launching a new service review section on this blog in collaboration with OrangeFren. These reviews are sponsored, yet the sponsorship does not influence the outcome of the evaluations. Reviews are done in advance, then, the service provider has the discretion to approve publication without modifications.
Sponsored reviews are independent from the kycnot.me list, being only part of the blog. The reviews have no impact on the scores of the listings or their continued presence on the list. Should any issues arise, I will not hesitate to remove any listing.
The review
WizardSwap is an instant exchange centred around privacy coins. It was launched in 2020 making it old enough to have weathered the 2021 bull run and the subsequent bearish year.
| Pros | Cons | |------|------| | Tor-friendly | Limited liquidity | | Guarantee of no KYC | Overly simplistic design | | Earn by providing liquidity | |
Rating: ★★★★★ Service Website: wizardswap.io
Liquidity
Right off the bat, we'll start off by pointing out that WizardSwap relies on its own liquidity reserves, meaning they aren't just a reseller of Binance or another exchange. They're also committed to a no-KYC policy, when asking them, they even promised they would rather refund a user their original coins, than force them to undergo any sort of verification.
On the one hand, full control over all their infrastructure gives users the most privacy and conviction about the KYC policies remaining in place.
On the other hand, this means the liquidity available for swapping isn't huge. At the time of testing we could only purchase at most about 0.73 BTC with XMR.
It's clear the team behind WizardSwap is aware of this shortfall and so they've come up with a solution unique among instant exchanges. They let you, the user, deposit any of the currencies they support into your account and earn a profit on the trades made using your liquidity.
Trading
Fees on WizardSwap are middle-of-the-pack. The normal fee is 2.2%. That's more than some exchanges that reserve the right to suddenly demand you undergo verification, yet less than half the fees on some other privacy-first exchanges. However as we mentioned in the section above you can earn almost all of that fee (2%) if you provide liquidity to WizardSwap.
It's good that with the current Bitcoin fee market their fees are constant regardless of how much, or how little, you send. This is in stark contrast with some of the alternative swap providers that will charge you a massive premium when attempting to swap small amounts of BTC away.
Test trades
Test trades are always performed without previous notice to the service provider.
During our testing we performed a few test trades and found that every single time WizardSwap immediately detected the incoming transaction and the amount we received was exactly what was quoted before depositing. The fees were inline with what WizardSwap advertises.

- Monero payment proof
- Bitcoin received
- Wizardswap TX link - it's possible that this link may cease to be valid at some point in the future.
ToS and KYC
WizardSwap does not have a Terms of Service or a Privacy Policy page, at least none that can be found by users. Instead, they offer a FAQ section where they addresses some basic questions.
The site does not mention any KYC or AML practices. It also does not specify how refunds are handled in case of failure. However, based on the FAQ section "What if I send funds after the offer expires?" it can be inferred that contacting support is necessary and network fees will be deducted from any refund.
UI & Tor
WizardSwap can be visited both via your usual browser and Tor Browser. Should you decide on the latter you'll find that the website works even with the most strict settings available in the Tor Browser (meaning no JavaScript).
However, when disabling Javascript you'll miss the live support chat, as well as automatic refreshing of the trade page. The lack of the first means that you will have no way to contact support from the trade page if anything goes wrong during your swap, although you can do so by mail.
One important thing to have in mind is that if you were to accidentally close the browser during the swap, and you did not save the swap ID or your browser history is disabled, you'll have no easy way to return to the trade. For this reason we suggest when you begin a trade to copy the url or ID to someplace safe, before sending any coins to WizardSwap.
The UI you'll be greeted by is simple, minimalist, and easy to navigate. It works well not just across browsers, but also across devices. You won't have any issues using this exchange on your phone.
Getting in touch
The team behind WizardSwap appears to be most active on X (formerly Twitter): https://twitter.com/WizardSwap_io
If you have any comments or suggestions about the exchange make sure to reach out to them. In the past they've been very receptive to user feedback, for instance a few months back WizardSwap was planning on removing DeepOnion, but the community behind that project got together ^1 and after reaching out WizardSwap reversed their decision ^2.
You can also contact them via email at:
support @ wizardswap . ioDisclaimer
None of the above should be understood as investment or financial advice. The views are our own only and constitute a faithful representation of our experience in using and investigating this exchange. This review is not a guarantee of any kind on the services rendered by the exchange. Do your own research before using any service.
-
 @ 39cc53c9:27168656
2025-05-27 09:21:46
@ 39cc53c9:27168656
2025-05-27 09:21:46Bitcoin enthusiasts frequently and correctly remark how much value it adds to Bitcoin not to have a face, a leader, or a central authority behind it. This particularity means there isn't a single person to exert control over, or a single human point of failure who could become corrupt or harmful to the project.
Because of this, it is said that no other coin can be equally valuable as Bitcoin in terms of decentralization and trustworthiness. Bitcoin is unique not just for being first, but also because of how the events behind its inception developed. This implies that, from Bitcoin onwards, any coin created would have been created by someone, consequently having an authority behind it. For this and some other reasons, some people refer to Bitcoin as "The Immaculate Conception".
While other coins may have their own unique features and advantages, they may not be able to replicate Bitcoin's community-driven nature. However, one other cryptocurrency shares a similar story of mystery behind its creation: Monero.
History of Monero
Bytecoin and CryptoNote
In March 2014, a Bitcointalk thread titled "Bytecoin. Secure, private, untraceable since 2012" was initiated by a user under the nickname "DStrange"^1^. DStrange presented Bytecoin (BCN) as a unique cryptocurrency, in operation since July 2012. Unlike Bitcoin, it employed a new algorithm known as CryptoNote.
DStrange apparently stumbled upon the Bytecoin website by chance while mining a dying bitcoin fork, and decided to create a thread on Bitcointalk^1^. This sparked curiosity among some users, who wondered how could Bytecoin remain unnoticed since its alleged launch in 2012 until then^2^.
Some time after, a user brought up the "CryptoNote v2.0" whitepaper for the first time, underlining its innovative features^4^. Authored by the pseudonymous Nicolas van Saberhagen in October 2013, the CryptoNote v2 whitepaper^5^ highlighted the traceability and privacy problems in Bitcoin. Saberhagen argued that these flaws could not be quickly fixed, suggesting it would be more efficient to start a new project rather than trying to patch the original^5^, an statement simmilar to the one from Satoshi Nakamoto^6^.
Checking with Saberhagen's digital signature, the release date of the whitepaper seemed correct, which would mean that Cryptonote (v1) was created in 2012^7^, although there's an important detail: "Signing time is from the clock on the signer's computer" ^9^.
Moreover, the whitepaper v1 contains a footnote link to a Bitcointalk post dated May 5, 2013^10^, making it impossible for the whitepaper to have been signed and released on December 12, 2012.
As the narrative developed, users discovered that a significant 80% portion of Bytecoin had been pre-mined^11^ and blockchain dates seemed to be faked to make it look like it had been operating since 2012, leading to controversy surrounding the project.
The origins of CryptoNote and Bytecoin remain mysterious, leaving suspicions of a possible scam attempt, although the whitepaper had a good amount of work and thought on it.
The fork
In April 2014, the Bitcointalk user
thankful_for_today, who had also participated in the Bytecoin thread^12^, announced plans to launch a Bytecoin fork named Bitmonero^13^.The primary motivation behind this fork was "Because there is a number of technical and marketing issues I wanted to do differently. And also because I like ideas and technology and I want it to succeed"^14^. This time Bitmonero did things different from Bytecoin: there was no premine or instamine, and no portion of the block reward went to development.
However, thankful_for_today proposed controversial changes that the community disagreed with. Johnny Mnemonic relates the events surrounding Bitmonero and thankful_for_today in a Bitcointalk comment^15^:
When thankful_for_today launched BitMonero [...] he ignored everything that was discussed and just did what he wanted. The block reward was considerably steeper than what everyone was expecting. He also moved forward with 1-minute block times despite everyone's concerns about the increase of orphan blocks. He also didn't address the tail emission concern that should've (in my opinion) been in the code at launch time. Basically, he messed everything up. Then, he disappeared.
After disappearing for a while, thankful_for_today returned to find that the community had taken over the project. Johnny Mnemonic continues:
I, and others, started working on new forks that were closer to what everyone else was hoping for. [...] it was decided that the BitMonero project should just be taken over. There were like 9 or 10 interested parties at the time if my memory is correct. We voted on IRC to drop the "bit" from BitMonero and move forward with the project. Thankful_for_today suddenly resurfaced, and wasn't happy to learn the community had assumed control of the coin. He attempted to maintain his own fork (still calling it "BitMonero") for a while, but that quickly fell into obscurity.
The unfolding of these events show us the roots of Monero. Much like Satoshi Nakamoto, the creators behind CryptoNote/Bytecoin and thankful_for_today remain a mystery^17^, having disappeared without a trace. This enigma only adds to Monero's value.
Since community took over development, believing in the project's potential and its ability to be guided in a better direction, Monero was given one of Bitcoin's most important qualities: a leaderless nature. With no single face or entity directing its path, Monero is safe from potential corruption or harm from a "central authority".
The community continued developing Monero until today. Since then, Monero has undergone a lot of technological improvements, migrations and achievements such as RingCT and RandomX. It also has developed its own Community Crowdfundinc System, conferences such as MoneroKon and Monerotopia are taking place every year, and has a very active community around it.
Monero continues to develop with goals of privacy and security first, ease of use and efficiency second. ^16^
This stands as a testament to the power of a dedicated community operating without a central figure of authority. This decentralized approach aligns with the original ethos of cryptocurrency, making Monero a prime example of community-driven innovation. For this, I thank all the people involved in Monero, that lead it to where it is today.
If you find any information that seems incorrect, unclear or any missing important events, please contact me and I will make the necessary changes.
Sources of interest
- https://forum.getmonero.org/20/general-discussion/211/history-of-monero
- https://monero.stackexchange.com/questions/852/what-is-the-origin-of-monero-and-its-relationship-to-bytecoin
- https://en.wikipedia.org/wiki/Monero
- https://bitcointalk.org/index.php?topic=583449.0
- https://bitcointalk.org/index.php?topic=563821.0
- https://bitcointalk.org/index.php?action=profile;u=233561
- https://bitcointalk.org/index.php?topic=512747.0
- https://bitcointalk.org/index.php?topic=740112.0
- https://monero.stackexchange.com/a/1024
- https://inspec2t-project.eu/cryptocurrency-with-a-focus-on-anonymity-these-facts-are-known-about-monero/
- https://medium.com/coin-story/coin-perspective-13-riccardo-spagni-69ef82907bd1
- https://www.getmonero.org/resources/about/
- https://www.wired.com/2017/01/monero-drug-dealers-cryptocurrency-choice-fire/
- https://www.monero.how/why-monero-vs-bitcoin
- https://old.reddit.com/r/Monero/comments/u8e5yr/satoshi_nakamoto_talked_about_privacy_features/
-
 @ 39cc53c9:27168656
2025-05-27 09:21:40
@ 39cc53c9:27168656
2025-05-27 09:21:40“The future is there... staring back at us. Trying to make sense of the fiction we will have become.” — William Gibson.
This month is the 4th anniversary of kycnot.me. Thank you for being here.
Fifteen years ago, Satoshi Nakamoto introduced Bitcoin, a peer-to-peer electronic cash system: a decentralized currency free from government and institutional control. Nakamoto's whitepaper showed a vision for a financial system based on trustless transactions, secured by cryptography. Some time forward and KYC (Know Your Customer), AML (Anti-Money Laundering), and CTF (Counter-Terrorism Financing) regulations started to come into play.
What a paradox: to engage with a system designed for decentralization, privacy, and independence, we are forced to give away our personal details. Using Bitcoin in the economy requires revealing your identity, not just to the party you interact with, but also to third parties who must track and report the interaction. You are forced to give sensitive data to entities you don't, can't, and shouldn't trust. Information can never be kept 100% safe; there's always a risk. Information is power, who knows about you has control over you.
Information asymmetry creates imbalances of power. When entities have detailed knowledge about individuals, they can manipulate, influence, or exploit this information to their advantage. The accumulation of personal data by corporations and governments enables extensive surveillances.
Such practices, moreover, exclude individuals from traditional economic systems if their documentation doesn't meet arbitrary standards, reinforcing a dystopian divide. Small businesses are similarly burdened by the costs of implementing these regulations, hindering free market competition^1:
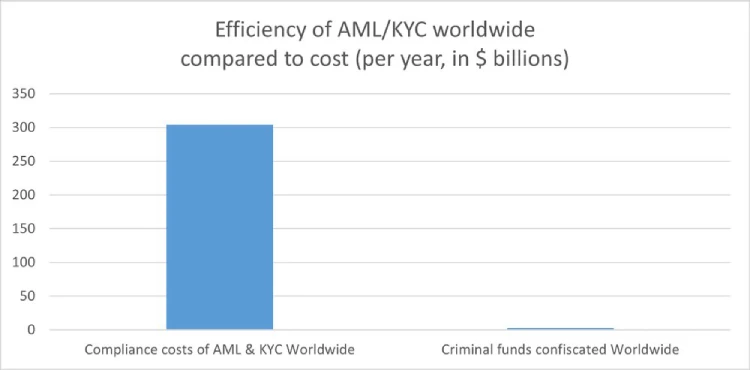
How will they keep this information safe? Why do they need my identity? Why do they force businesses to enforce such regulations? It's always for your safety, to protect you from the "bad". Your life is perpetually in danger: terrorists, money launderers, villains... so the government steps in to save us.
‟Hush now, baby, baby, don't you cry Mamma's gonna make all of your nightmares come true Mamma's gonna put all of her fears into you Mamma's gonna keep you right here, under her wing She won't let you fly, but she might let you sing Mamma's gonna keep baby cosy and warm” — Mother, Pink Floyd
We must resist any attack on our privacy and freedom. To do this, we must collaborate.
If you have a service, refuse to ask for KYC; find a way. Accept cryptocurrencies like Bitcoin and Monero. Commit to circular economies. Remove the need to go through the FIAT system. People need fiat money to use most services, but we can change that.
If you're a user, donate to and prefer using services that accept such currencies. Encourage your friends to accept cryptocurrencies as well. Boycott FIAT system to the greatest extent you possibly can.
This may sound utopian, but it can be achieved. This movement can't be stopped. Go kick the hornet's nest.
“We must defend our own privacy if we expect to have any. We must come together and create systems which allow anonymous transactions to take place. People have been defending their own privacy for centuries with whispers, darkness, envelopes, closed doors, secret handshakes, and couriers. The technologies of the past did not allow for strong privacy, but electronic technologies do.” — Eric Hughes, A Cypherpunk's Manifesto
The anniversary
Four years ago, I began exploring ways to use crypto without KYC. I bookmarked a few favorite services and thought sharing them to the world might be useful. That was the first version of kycnot.me — a simple list of about 15 services. Since then, I've added services, rewritten it three times, and improved it to what it is now.
kycnot.me has remained 100% independent and 100% open source^2 all these years. I've received offers to buy the site, all of which I have declined and will continue to decline. It has been DDoS attacked many times, but we made it through. I have also rewritten the whole site almost once per year (three times in four years).
The code and scoring algorithm are open source (contributions are welcome) and I can't arbitrarly change a service's score without adding or removing attributes, making any arbitrary alterations obvious if they were fake. You can even see the score summary for any service's score.
I'm a one-person team, dedicating my free time to this project. I hope to keep doing so for many more years. Again, thank you for being part of this.
-
 @ cae03c48:2a7d6671
2025-05-28 04:00:33
@ cae03c48:2a7d6671
2025-05-28 04:00:33Bitcoin Magazine
Steak ‘n Shake Reveals Bitcoin Payment Success at Bitcoin 2025 ConferenceSpeaking at the Bitcoin 2025 Conference this morning, Steak ‘n Shake executive Dan Edwards shared new data and insights from the company’s recent move to accept Bitcoin payments globally via the Lightning Network.
JUST IN: Fast food giant Steak 'n Shake announced they're saving 50% in processing fees accepting Bitcoin payments

'#Bitcoin is faster than credit cards'
 pic.twitter.com/bxApgBL6El
pic.twitter.com/bxApgBL6El— Bitcoin Magazine (@BitcoinMagazine) May 27, 2025
“On May 16, we began accepting Bitcoin as payment in all of our locations where permitted to do so by law,” Edwards began. “This is a global implementation.”
According to Edwards, Bitcoin transactions are already outperforming expectations. “The day we launched Bitcoin, 1 out of every 500 bitcoin transactions in the world happened at Steak ‘n Shake,” he said.
Steak ‘n Shake is also saving significantly on processing fees. “Bitcoin is faster than credit cards, and when customers choose to pay in Bitcoin, we’re saving 50% in processing fees,” said Edwards. “That makes Bitcoin a win for the customer, a win for us, and a win for the Bitcoin community.”
He emphasized that the decision was not a publicity stunt, but a serious payment upgrade. “We didn’t see this as a marketing gimmick. We saw it as a viable option to pay—on par with other globally accepted methods.”
The company reports that customer behavior has already shifted. “We’ve seen a sustained spike since adding Bitcoin,” Edwards noted.
Edwards also teased the company’s future plans, calling for more technical talent. “We’re not done. We’re investing in cyber chefs, autonomous drives, AI tech—and we need engineers to help us build it.”
To celebrate Bitcoin integration, limited-edition Bitcoin-themed menu items are launching this week in Las Vegas, including the Bitcoin Burger, Super-Sized Bitcoin Meal, and Bitcoin Milkshake. A “blockchain menu” is also in the works.
“Celebrate the use of Bitcoin,” Edwards concluded. “Because this is just the beginning.”
This post Steak ‘n Shake Reveals Bitcoin Payment Success at Bitcoin 2025 Conference first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ 33baa074:3bb3a297
2025-05-28 02:26:55
@ 33baa074:3bb3a297
2025-05-28 02:26:55The PH value of a swimming pool is one of the important indicators for measuring the quality of swimming pool water. Its importance is mainly reflected in the following aspects:
Affecting human comfort The pH of water that the human body is most adapted to is neutral. Inappropriate pH of swimming pool water will irritate human skin, eyes and mucous membranes, causing discomfort. For example, when the pH value is high or low, it may irritate the swimmer's skin, eyes, etc., causing discomfort such as itchy skin, red and swollen eyes, and sticky hair, affecting the swimmer's physical health and swimming experience.
 Affecting the disinfection effect of swimming pools
Affecting the activity of chlorine disinfectants
Swimming pools are usually disinfected with chlorine-containing disinfectants. Different pH values will cause differences in the activity and disinfection ability of chlorine. When the pH value in swimming pool water is greater than 8.0, the activity of chlorine disinfectants in water will be significantly reduced, that is, the disinfection ability will be reduced, which will affect the algae removal and sterilization effects, resulting in the proliferation of green algae in swimming pool water. When the pH value is less than 7.0, the activity of the disinfectant in the swimming pool will be relatively high, the residual chlorine in the swimming pool will dissipate faster, and the disinfection durability of the swimming pool disinfectant will be greatly weakened. Under the condition of pH about 7.5, there is a relatively good disinfection effect and the duration of the drug effect is relatively long.
Affecting the disinfection effect of swimming pools
Affecting the activity of chlorine disinfectants
Swimming pools are usually disinfected with chlorine-containing disinfectants. Different pH values will cause differences in the activity and disinfection ability of chlorine. When the pH value in swimming pool water is greater than 8.0, the activity of chlorine disinfectants in water will be significantly reduced, that is, the disinfection ability will be reduced, which will affect the algae removal and sterilization effects, resulting in the proliferation of green algae in swimming pool water. When the pH value is less than 7.0, the activity of the disinfectant in the swimming pool will be relatively high, the residual chlorine in the swimming pool will dissipate faster, and the disinfection durability of the swimming pool disinfectant will be greatly weakened. Under the condition of pH about 7.5, there is a relatively good disinfection effect and the duration of the drug effect is relatively long.Influence on the existence form of residual chlorine Depending on the pH value, free chlorine may be chlorine gas (Cl₂), chlorophyll acid (HClO) or hypocrite ion (ClO⁻) dissolved in water. The disinfection effect of HClO is about 100 times stronger than that of ClO⁻. When the pH value is about 7.5, both chlorophyll acid and hypocrite ion exist, and the proportion is roughly equal, which can ensure a better disinfection effect.
Corrosion to swimming pool facilities Pool water acidity or alkalinity will have a corrosive effect on swimming pool equipment. If the water is acidic, it will also corrode the accessories of the suction machine and affect the normal use of the equipment. If the pH value is unbalanced for a long time, the chemical disinfectants in the swimming pool will corrode the pool structure and swimming pool equipment, which will not only affect the appearance of the pool structure and equipment, but also shorten the service life of the swimming pool and increase the maintenance cost of the swimming pool in the later stage.
Impact on the containment of pool water The pH value in the swimming pool will change due to many external factors, such as rain, the use of swimming pool disinfectants, and alkaline chemicals. Maintaining a suitable pH value can make the pool water have better containment, more stably cope with the influence of these external factors, and maintain the relative stability of water quality.
In summary, the pH value of the swimming pool is of great significance to ensure the health and comfort of swimmers, ensure the disinfection effect, protect swimming pool facilities, and maintain the stability of pool water quality.
-
 @ 39cc53c9:27168656
2025-05-27 09:21:37
@ 39cc53c9:27168656
2025-05-27 09:21:37After almost 3 months of work, we've completed the redesign of kycnot.me. More modern and with many new features.
Privacy remains the foundation - everything still works with JavaScript disabled. If you enable JS, you will get some nice-to-have features like lazy loading and smoother page transitions, but nothing essential requires it.
User Accounts
We've introduced user accounts that require zero personal information:
- Secret user tokens - no email, no phone number, no personal data
- Randomly generated usernames for default privacy and fairness
- Karma system that rewards contributions and unlocks features: custom display names, profile pictures, and more.
Reviews and Community Discussions
On the previous sites, I was using third party open source tools for the comments and discussions. This time, I've built my own from scratch, fully integrated into the site, without JavaScript requirements.
Everyone can share their experiences and help others make informed decisions:
- Ratings: Comments can have a 1-5 star rating attached. You can have one rating per service and it will affect the overall user score.
- Discussions: These are normal comments, you can add them on any listed service.
Comment Moderation
I was strugling to keep up with moderation on the old site. For this, we've implemented an AI-powered moderation system that:
- Auto-approves legitimate comments instantly
- Flags suspicious content for human review
- Keeps discussions valuable by minimizing spam
The AI still can mark comments for human review, but most comments will get approved automatically by this system. The AI also makes summaries of the comments to help you understand the overall sentiment of the community.
Powerful Search & Filtering
Finding exactly what you need is now easier:
- Advanced filtering system with many parameters. You can even filter by attributes to pinpoint services with specific features.
The results are dynamic and shuffle services with identical scores for fairness.
See all listings
Listings are now added as 'Community Contributed' by default. This means that you can still find them in the search results, but they will be clearly marked as such.
Updated Scoring System
New dual-score approach provides more nuanced service evaluations:
- Privacy Score: Measures how well a service protects your personal information and data
-
Trust Score: Assesses reliability, security, and overall reputation
-
Combined into a weighted Overall Score for quick comparisons
- Completely transparent and open source calculation algorithm. No manual tweaking or hidden factors.
AI-Powered Terms of Service Analysis
Basically, a TLDR summary for Terms of Service:
- Automated system extracts the most important points from complex ToS documents
- Clear summaries
- Updated monthly to catch any changes
The ToS document is hashed and only will be updated if there are any changes.
Service Events and Timelines
Track the complete history of any service, on each service page you can see the timeline of events. There are two types of events:
- Automatic events: Created by the system whenever something about a service changes, like its description, supported currencies, attributes, verification status…
- Manual events: Added by admins when there’s important news, such as a service going offline, being hacked, acquired, shut down, or other major updates.
There is also a global timeline view available at /events
Notification System
Since we now have user accounts, we built a notifiaction system so you can stay informed about anything:
- Notifications for comment replies and status changes
- Watch any comment to get notified for new replies.
- Subscribe to services to monitor events and updates
- Notification customization.
Coming soon: Third-party privacy-preserving notifications integration with Telegram, Ntfy.sh, webhooks...
Service Suggestions
Anyone with an account can suggest a new service via the suggestion form. After submitting, you'll receive a tracking page where you can follow the status of your suggestion and communicate directly with admins.
All new suggestions start as "unlisted" — they won't appear in search results until reviewed. Our team checks each submission to ensure it's not spam or inappropriate. If similar services already exist, you'll be shown possible duplicates and can choose to submit your suggestion as an edit instead.
You can always check the progress of your suggestion, respond to moderator questions, and see when it goes live, everything will also be notified to your account. This process ensures high-quality listings and a collaborative approach to building the directory.
These are some of the main features we already have, but there are many more small changes and improvements that you will find when using the site.
What's Next?
This is just the beginning. We will be constantly working to improve KYCnot.me and add more features that help you preserve your privacy.
Remember: True financial freedom requires the right to privacy. Stay KYC-free!
-
 @ 5ea46480:450da5bd
2025-05-27 08:23:58
@ 5ea46480:450da5bd
2025-05-27 08:23:58Understanding or grasping Nostr can be deceptively difficult. At the very least it is non-trivial. At first glance, looking at NIP-01, the protocol is rather straight forward. But those are just the basics; yes the beauty of Nostr is its ‘simplicity’, but that does not mean the system that results from it is not complex. Conway's Game of Life only has a hand full of rules, yet you can, in theory at least, create any complex system imaginable. And this is where the deception lies; the less you define from the outset, the more you imply on what follows.
It appears that as it stands, Nostr suffers from this deceptiveness. You can reason through all these implications, but that is still an exercise that has to be performed and where mistakes can be made. Worse, this exercise has been a group effort from the start that is still in progress. Currently there is no clear cut ‘authoritative’ example of all the implications that have been ‘discovered’ thus far.
A good example of the implications following Nostr’s primitives is what we now refer to as the ‘outbox model’. The reason we ‘now’ refer to it as such, is because initially it was called the ‘Gossip model’ derived from the client that first implemented the idea. Outbox is fundamental to Nostr, but it was never explicitly stated in the initial protocol description. The result is that roughly five years into this Nostr endeavor, it is still not universally implemented; worse yet, some developers appear to be in no rush to do so. Now the reason they will give you is probably one based on priority, yet I can’t shake the feeling that they apparently don’t ‘get it’.
My point here is not to play some blame game or hold anyone to account. I am just concluding they don’t actually get the new paradigm that we have all stumbled into. To expand on this specific outbox example, its significance only becomes really apparent further along in the ‘reasoning through all the implications’ exercise. In relation to one aspect, but there are more: The point is not ‘just’ censorship-resistance for users, but the freedom for relays that comes with it to apply whatever policy on what they store and make available; it is this discrimination or curation that can add value by making finding relevant information easier in a straightforward manner. But it relies on outbox to avoid isolation; something that only becomes apparent once you are reasoning through all the implications on how we discover and consume content.
To be clear, this piece is not supposed to a crusade on the outbox model, my point here is that there is an inherent logic to Nostr stemming from putting cryptography front and center. It is a logic that has to be applied and will subsequently carry you through all the challenges we face in reconstructing the entirety of the web. This is not to say there is only one obvious path, and different schools of thought are bound to emerge. But it behooves us all, faced with this new paradigm, to continuously reflect on the mental image we have cultivated of what Nostr is; actively re-performing that exercise of exploring the implications this simple set of protocol rules creates.
Unfortunately I can not escape my own folly. After all, I am just an armchair asshole that never wrote a single line of code in his life. Obviously this minds-eye bullshit is not even half the story, the bulk of the effort is translating it into software, the tangible, the real. It is in that effort ultimately the real exploration of this paradigm occurs. All I can do is build castles in the sky.
-
 @ b7274d28:c99628cb
2025-05-27 07:07:33
@ b7274d28:c99628cb
2025-05-27 07:07:33A few months ago, a nostrich was switching from iOS to Android and asked for suggestions for #Nostr apps to try out. nostr:npub18ams6ewn5aj2n3wt2qawzglx9mr4nzksxhvrdc4gzrecw7n5tvjqctp424 offered the following as his response:
nostr:nevent1qvzqqqqqqypzq0mhp4ja8fmy48zuk5p6uy37vtk8tx9dqdwcxm32sy8nsaa8gkeyqydhwumn8ghj7un9d3shjtnwdaehgunsd3jkyuewvdhk6tcpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhszythwden5te0dehhxarj9emkjmn99uqzpwwts6n28eyvjpcwvu5akkwu85eg92dpvgw7cgmpe4czdadqvnv984rl0z
Yes. #Android users are fortunate to have some powerful Nostr apps and tools at our disposal that simply have no comparison over on the iOS side. However, a tool is only as good as the knowledge of the user, who must have an understanding of how best to wield it for maximum effect. This fact was immediately evidenced by replies to Derek asking, "What is the use case for Citrine?" and "This is the first time I'm hearing about Citrine and Pokey. Can you give me links for those?"
Well, consider this tutorial your Nostr starter-kit for Android. We'll go over installing and setting up Amber, Amethyst, Citrine, and Pokey, and as a bonus we'll be throwing in the Zapstore and Coinos to boot. We will assume no previous experience with any of the above, so if you already know all about one or more of these apps, you can feel free to skip that tutorial.
So many apps...
You may be wondering, "Why do I need so many apps to use Nostr?" That's perfectly valid, and the honest answer is, you don't. You can absolutely just install a Nostr client from the Play Store, have it generate your Nostr identity for you, and stick with the default relays already set up in that app. You don't even need to connect a wallet, if you don't want to. However, you won't experience all that Nostr has to offer if that is as far as you go, any more than you would experience all that Italian cuisine has to offer if you only ever try spaghetti.
Nostr is not just one app that does one thing, like Facebook, Twitter, or TikTok. It is an entire ecosystem of applications that are all built on top of a protocol that allows them to be interoperable. This set of tools will help you make the most out of that interoperability, which you will never get from any of the big-tech social platforms. It will provide a solid foundation for you to build upon as you explore more and more of what Nostr has to offer.
So what do these apps do?

Fundamental to everything you do on Nostr is the need to cryptographically sign with your private key. If you aren't sure what that means, just imagine that you had to enter your password every time you hit the "like" button on Facebook, or every time you commented on the latest dank meme. That would get old really fast, right? That's effectively what Nostr requires, but on steroids.
To keep this from being something you manually have to do every 5 seconds when you post a note, react to someone else's note, or add a comment, Nostr apps can store your private key and use it to sign behind the scenes for you. This is very convenient, but it means you are trusting that app to not do anything with your private key that you don't want it to. You are also trusting it to not leak your private key, because anyone who gets their hands on it will be able to post as you, see your private messages, and effectively be you on Nostr. The more apps you give your private key to, the greater your risk that it will eventually be compromised.
Enter #Amber, an application that will store your private key in only one app, and all other compatible Nostr apps can communicate with it to request a signature, without giving any of those other apps access to your private key.
Most Nostr apps for Android now support logging in and signing with Amber, and you can even use it to log into apps on other devices, such as some of the web apps you use on your PC. It's an incredible tool given to us by nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5, and only available for Android users. Those on iPhone are incredibly jealous that they don't have anything comparable, yet.

Speaking of nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5, the next app is also one of his making.
All Nostr data is stored on relays, which are very simple servers that Nostr apps read notes from and write notes to. In most forms of social media, it can be a pain to get your own data out to keep a backup. That's not the case on Nostr. Anyone can run their own relay, either for the sake of backing up their personal notes, or for others to post their notes to, as well.
Since Nostr notes take up very little space, you can actually run a relay on your phone. I have been on Nostr for almost 2 and a half years, and I have 25,000+ notes of various kinds on my relay, and a backup of that full database is just 24MB on my phone's storage.
Having that backup can save your bacon if you try out a new Nostr client and it doesn't find your existing follow list for some reason, so it writes a new one and you suddenly lose all of the people you were following. Just pop into your #Citrine relay, confirm it still has your correct follow list or import it from a recent backup, then have Citrine restore it. Done.
Additionally, there are things you may want to only save to a relay you control, such as draft messages that you aren't ready to post publicly, or eCash tokens, which can actually be saved to Nostr relays now. Citrine can also be used with Amber for signing into certain Nostr applications that use a relay to communicate with Amber.
If you are really adventurous, you can also expose Citrine over Tor to be used as an outbox relay, or used for peer-to-peer private messaging, but that is far more involved than the scope of this tutorial series.

You can't get far in Nostr without a solid and reliable client to interact with. #Amethyst is the client we will be using for this tutorial because there simply isn't another Android client that comes close, so far. Moreover, it can be a great client for new users to get started on, and yet it has a ton of features for power-users to take advantage of as well.
There are plenty of other good clients to check out over time, such as Coracle, YakiHonne, Voyage, Olas, Flotilla and others, but I keep coming back to Amethyst, and by the time you finish this tutorial, I think you'll see why. nostr:npub1gcxzte5zlkncx26j68ez60fzkvtkm9e0vrwdcvsjakxf9mu9qewqlfnj5z and others who have contributed to Amethyst have really built something special in this client, and it just keeps improving with every update that's shipped.

Most social media apps have some form of push notifications, and some Nostr apps do, too. Where the issue comes in is that Nostr apps are all interoperable. If you have more than one application, you're going to have both of them notifying you. Nostr users are known for having five or more Nostr apps that they use regularly. If all of them had notifications turned on, it would be a nightmare. So maybe you limit it to only one of your Nostr apps having notifications turned on, but then you are pretty well locked-in to opening that particular app when you tap on the notification.
Pokey, by nostr:npub1v3tgrwwsv7c6xckyhm5dmluc05jxd4yeqhpxew87chn0kua0tjzqc6yvjh, solves this issue, allowing you to turn notifications off for all of your Nostr apps, and have Pokey handle them all for you. Then, when you tap on a Pokey notification, you can choose which Nostr app to open it in.
Pokey also gives you control over the types of things you want to be notified about. Maybe you don't care about reactions, and you just want to know about zaps, comments, and direct messages. Pokey has you covered. It even supports multiple accounts, so you can get notifications for all the npubs you control.

One of the most unique and incredibly fun aspects of Nostr is the ability to send and receive #zaps. Instead of merely giving someone a 👍️ when you like something they said, you can actually send them real value in the form of sats, small portions of a Bitcoin. There is nothing quite like the experience of receiving your first zap and realizing that someone valued what you said enough to send you a small amount (and sometimes not so small) of #Bitcoin, the best money mankind has ever known.
To be able to have that experience, though, you are going to need a wallet that can send and receive zaps, and preferably one that is easy to connect to Nostr applications. My current preference for that is Alby Hub, but not everyone wants to deal with all that comes along with running a #Lightning node. That being the case, I have opted to use nostr:npub1h2qfjpnxau9k7ja9qkf50043xfpfy8j5v60xsqryef64y44puwnq28w8ch for this tutorial, because they offer one of the easiest wallets to set up, and it connects to most Nostr apps by just copy/pasting a connection string from the settings in the wallet into the settings in your Nostr app of choice.
Additionally, even though #Coinos is a custodial wallet, you can have it automatically transfer any #sats over a specified threshold to a separate wallet, allowing you to mitigate the custodial risk without needing to keep an eye on your balance and make the transfer manually.

Most of us on Android are used to getting all of our mobile apps from one souce: the Google Play Store. That's not possible for this tutorial series. Only one of the apps mentioned above is available in Google's permissioned playground. However, on Android we have the advantage of being able to install whatever we want on our device, just by popping into our settings and flipping a toggle. Indeed, thumbing our noses at big-tech is at the heart of the Nostr ethos, so why would we make ourselves beholden to Google for installing Nostr apps?
The nostr:npub10r8xl2njyepcw2zwv3a6dyufj4e4ajx86hz6v4ehu4gnpupxxp7stjt2p8 is an alternative app store made by nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9 as a resource for all sorts of open-source apps, but especially Nostr apps. What is more, you can log in with Amber, connect a wallet like Coinos, and support the developers of your favorite Nostr apps directly within the #Zapstore by zapping their app releases.
One of the biggest features of the Zapstore is the fact that developers can cryptographically sign their app releases using their Nostr keys, so you know that the app you are downloading is the one they actually released and hasn't been altered in any way. The Zapstore will warn you and won't let you install the app if the signature is invalid.
Getting Started
Since the Zapstore will be the source we use for installing most of the other apps mentioned, we will start with installing the Zapstore.
We will then use the Zapstore to install Amber and set it up with our Nostr account, either by creating a new private key, or by importing one we already have. We'll also use it to log into the Zapstore.
Next, we will install Amethyst from the Zapstore and log into it via Amber.
After this, we will install Citrine from the Zapstore and add it as a local relay on Amethyst.
Because we want to be able to send and receive zaps, we will set up a wallet with CoinOS and connect it to Amethyst and the Zapstore using Nostr Wallet Connect.
Finally, we will install Pokey using the Zapstore, log into it using Amber, and set up the notifications we want to receive.
By the time you are done with this series, you will have a great head-start on your Nostr journey compared to muddling through it all on your own. Moreover, you will have developed a familiarity with how things generally work on Nostr that can be applied to other apps you try out in the future.
Continue to Part 2: The Zapstore. Nostr Link: nostr:naddr1qvzqqqr4gupzpde8f55w86vrhaeqmd955y4rraw8aunzxgxstsj7eyzgntyev2xtqydhwumn8ghj7un9d3shjtnzwf5kw6r5vfhkcapwdejhgtcqp5cnwdphxv6rwwp3xvmnzvqgty5au