-
 @ c9badfea:610f861a
2025-05-20 19:49:20
@ c9badfea:610f861a
2025-05-20 19:49:20- Install Sky Map (it's free and open source)
- Launch the app and tap Accept, then tap OK
- When asked to access the device's location, tap While Using The App
- Tap somewhere on the screen to activate the menu, then tap ⁝ and select Settings
- Disable Send Usage Statistics
- Return to the main screen and enjoy stargazing!
ℹ️ Use the 🔍 icon in the upper toolbar to search for a specific celestial body, or tap the 👁️ icon to activate night mode
-
 @ 04c915da:3dfbecc9
2025-05-20 15:53:48
@ 04c915da:3dfbecc9
2025-05-20 15:53:48This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ 662f9bff:8960f6b2
2025-05-20 18:52:01
@ 662f9bff:8960f6b2
2025-05-20 18:52:01April already and we are still refugees from the madness in HK. During March I had quite a few family matters that took priority and I also needed to work for two weeks. April is a similar schedule but we flew to Madeira for a change of scene and so that I could have a full 2-weeks off - my first real holiday in quite a few years!
We are staying in an airBnB in Funchal - an experience that I can totally recommend - video below! Nice to have an apartment that is fully equipped in a central location and no hassle for a few weeks. While here we are making the most of the great location and all the local possibiliites.
Elsewhere in the world
Things are clearly not going great around the world. If you are still confused as to why these things are happening, do go back and read the previous Letter from HK section "Why? How did we get here?"
You should be in no doubt that the "Great Reset" with its supporting "Great Narrative" is in full swing.. This is it - it is not a drill. For additional insights the following are recommended.
-
Jeff Booth discusses clearly and unemotionally with Pomp - Inflation is theft from humanity by the world governments
-
James' summary of Day 2 of the Miami conference - Peter Thiel (wow) and a fantastic explainer from Saifedean on the costs of the current corrupt financial system
-
James' summary of Day 3 of the Miami conference - listen in particular to the words of wisdom from Michael Saylor and Lyn Alden
-
Layered Money - The corruption of the system will blow your mind once you understand it…
-
This is BIG: Strike Is Bringing Freedom To Retail Merchants
-
Mark summarises Ray's book: Things will go faster and slower than you want!
-
Thoughtful words from George - evil is at work - be in no doubt..
-
Wow - My mind is blown. Must listen to John Carvalho - what clear ambition and answers to every question!
-
Related to the John Carvalho discussion. Likely these two options will end up complementing each other
On the personal and inspirational side
Advantage of time off work is that I have more time to read, listen and watch things that interest me. It really is a privilege that so much high quality material is so readily available. Do not let it go to waste. A few fabulous finds (and some re-finds) from this past week:
-
Ali Abdaal's bookshelf review just blew my mind! For the full list of books with links see the text under his video. So many inspirations and his delivery is perfect.
-
Gotta recommend Ali's 21 Life Lessons. I have been following him since he was student in Cambridge five years ago - his personal and professional growth and what he achieves (now with his team) is truely staggering.
-
Also his 15 books to read in 2022 - especially this one!
-
I also keep going back to Steve Jobs giving the 2005 Stanford Commencement address Three stories from his life - listen and be inspired - especially story #3
You will know that I am a fan of Audio Books and also Kindle - recently I am starting to use Whispersync where you get the Kindle- and Audio-books together for a nice price. This makes it easier to take notes (using Mac or iPad Kindle reader) while getting the benefit of having the book read to you by a professional reader.
I have also been inspired by a few people pushing themselves to do more reading - like this girl and Ali himself with his tips. Above all: just do it and do not get stuck on something that does not work for you!
Books that I am reading - Audio and Kindle!
-
The Final Empire: Mistborn, Book 1 - this is a new genre for me - I rather feel that it might be a bit too complicated for my engineering mind - let's see
-
Die with Zero: Getting All You Can from Your Money and Your Life - certainly provocative and obvious if you think about it but 99% do the opposite!
-
Chariots of the Gods - a classic by Erich von Daniken (written in 1968) - I have been inspired by his recent YT video appearances. Thought provoking and leads you to many possibilities.
So what's it like in Funchal, Madeira?
Do check out HitTheRoadMadeira's walking tour around Funchal
My first impressions of Funchal
and see my day out on Thursday!
Saturday - Funchal and Camar de Lobos
That's it!
No one can be told what The Matrix is.\ You have to see it for yourself.**
Do share this newsletter with any of your friends and family who might be interested.
You can also email me at: LetterFrom@rogerprice.me
💡Enjoy the newsletters in your own language : Dutch, French, German, Serbian, Chinese Traditional & Simplified, Thai and Burmese.
-
-
 @ 05a0f81e:fc032124
2025-05-20 18:26:00
@ 05a0f81e:fc032124
2025-05-20 18:26:00The term "Ponzi scheme" is named after Charles Ponzi, who famously perpetrated a large-scale fraudulent investment scheme in the 1920s. While earlier instances of similar schemes existed, Ponzi's notoriety and scale cemented the name in popular usage.
There are some detailed of ponzi history: Pre-Ponzi; Adele Spitzeder (1869-1872): In Germany, Spitzeder used a Ponzi-like scheme to defraud investors.
Sarah Howe (1880s): In the United States, Howe used a scheme called "Ladies Deposit" to attract female investors with high interest rates, ultimately stealing their money.
Literary Precedents: Charles Dickens novels "Martin Chuzzlewit" (1844) and "Little Dorrit" (1857) included characters and storylines that featured similar fraudulent investment schemes.
The Charles Ponzi Scheme (1920s): Ponzi's scheme involved claiming to buy international postal reply coupons in Europe, redeem them for more expensive US postage stamps, and generate high profits.
The Reality: In reality, he diverted money from new investors to pay off earlier investors, rather than using it for legitimate business.
The Rise and Fall: Ponzi amassed significant wealth, drawing in around 30,000 investors and collecting over $8 million in just seven months. However, the scheme collapsed due to its unsustainable nature, and Ponzi was eventually convicted and served time in prison.
Impact and Legacy: Ponzi's scheme gained widespread publicity, both during its operation and after its collapse. This notoriety led to the scheme being named after him, and the term "Ponzi scheme" became synonymous with this type of fraudulent investment scam.
Ponzi scheme have cause more harm than good in world at large and it is a fraudulent investment scheme. Say no to ponzi scheme! Say no to ponzi scheme!!
-
 @ 04c915da:3dfbecc9
2025-05-20 15:47:16
@ 04c915da:3dfbecc9
2025-05-20 15:47:16Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 57c631a3:07529a8e
2025-05-20 15:40:04
@ 57c631a3:07529a8e
2025-05-20 15:40:04The Video: The World's Biggest Toddler
https://connect-test.layer3.press/articles/3f9d28a4-0876-4ee8-bdac-d1a56fa9cd02
-
 @ c7e8fdda:b8f73146
2025-05-17 21:24:18
@ c7e8fdda:b8f73146
2025-05-17 21:24:18Weekend Video: May 17th, 2025 Good Saturday! Today’s weekend video for our paid subscribers is out! I talk about generally most of what occurred this week including:
More of the Qatari Jet stupidity
Ukraine Saga re negotiations
Trump’s very not corrupt at all trip to the Middle East
Trump’s plan he’s shopping for Gaza
His meeting with the new Syrian leader
How he has fallen prostrate be…
Read more https://connect-test.layer3.press/articles/19c5f7cc-f59d-450e-9dd4-743b6b42d276
-
 @ c9badfea:610f861a
2025-05-20 17:05:41
@ c9badfea:610f861a
2025-05-20 17:05:41- Install YTDLnis (it's free and open source)
- Launch the app and allow notifications and storage access if prompted
- Go to any supported website or use the YouTube, Instagram, X, or Facebook app
- Tap Share on the post or website URL and select YTDLnis as the sharing destination
- Adjust the settings if desired and tap Download
- You'll be notified when the download finishes
- Enjoy uninterrupted watching!
ℹ️ This app uses
yt-dlpinternally and it's also available as a standalone CLI tool -
 @ 0971cd37:53c969f4
2025-05-20 17:00:53
@ 0971cd37:53c969f4
2025-05-20 17:00:53ลดต้นทุนค่าไฟ เพิ่มความคุ้มค่าให้การขุด Bitcoin ที่บ้าน ในยุคที่ต้นทุนพลังงานสูงขึ้นอย่างต่อเนื่อง นักขุด Bitcoin ที่บ้าน หรือ Home Miner ต้องคิดให้รอบคอบก่อนเลือกเครื่องขุด เพราะ “แรงขุดสูงสุด” ไม่ได้แปลว่า “กำไรดีที่สุด” อีกต่อไป การเลือกเครื่องขุดไม่ใช่แค่ดูแค่แรงขุด (Hashrate) สูงสุดเท่านั้น แต่ต้องพิจารณาเรื่อง "การกินไฟ" และ "ความคุ้มค่าในการใช้งานระยะยาว" ด้วย ซึ่งสายหนึ่งที่ได้รับความนิยมมากขึ้นเรื่อย ๆ ก็คือ สาย Tuning Power หรือการจูนเครื่องขุดเพื่อให้ได้อัตราส่วน Hashrate/Watt ที่ดีที่สุด
เทรนด์ใหม่ของวงการขุดคือสาย Tuning Power หรือการปรับแต่งพลังงานของเครื่องขุด Bitcoin (ASIC) ให้ได้ ประสิทธิภาพ Hashrate ต่อการใช้พลังงาน (Efficiency) สูงที่สุด ซึ่งเหมาะอย่างยิ่งสำหรับการขุดในบ้านที่มีข้อจำกัดด้านค่าไฟ ความร้อน และ เสียงรบกวน
Tuning Power คืออะไร? Tuning Power คือการปรับลดแรงขุดของเครื่อง ASIC ลงเล็กน้อย เพื่อให้กินไฟน้อยลงแบบชัดเจน
ตัวอย่างเช่น Custom Firmware Braiins OS ใช้กับ Antminer S19jpro จากเดิมแรงขุด 104 TH/s กินไฟ 3,500W เมื่อปรับแต่งในส่วน Power Target จูนเหลือ 75 TH/s อาจกินไฟแค่ 1,600W-1,800W หลังจาก Tuning ค่าประสิทธิภาพ(Efficiency)ดีขึ้น เช่น จาก 32 J/TH เหลือเพียง 22–20 J/TH
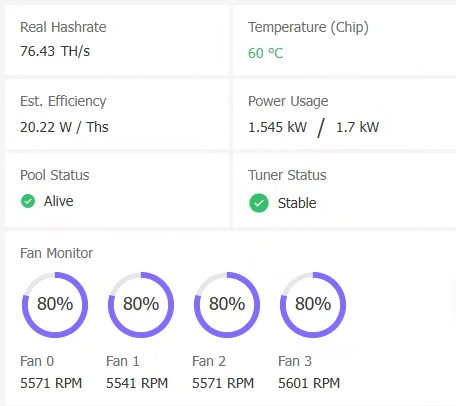 หมายเหตุ: ค่า Efficiency ยิ่งต่ำ ยิ่งดี แปลว่าใช้พลังงานน้อยต่อ 1 TH
หมายเหตุ: ค่า Efficiency ยิ่งต่ำ ยิ่งดี แปลว่าใช้พลังงานน้อยต่อ 1 THทำไมต้อง Tuning Power? การจูนพลังงาน (Tuning Power) คือการปรับแต่งเครื่องขุด เช่น ASIC ให้ทำงานที่แรงขุดไม่เต็ม 100% แต่กินไฟน้อยลงอย่างชัดเจน ส่งผลให้:
- ประหยัดค่าไฟ โดยเฉพาะถ้าขุดในพื้นที่ต้นทุนพลังงานค่าไฟสูงหรือไม่มี TOU (Time of Use) และ เหมาะสำหรับผู้ใช้ไฟแบบ TOU ที่ค่าไฟกลางวัน ON-Peak แพง ต้องการขุดเลือกช่วงกลางคืนและวันหยุดเสาร์-อาทิตย์ และ วันหยุดราชการตามปกติ Off-Peak , ที่ใช้ระบบ Solar หรือมีระบบ Battery ต้องการประหยัดไฟ
- ลดความร้อนของเครื่อง ทำให้ยืดอายุการใช้งานและลดค่าใช้จ่ายด้าน ซำบำรุง ระบบระบายความร้อน
- เพิ่มความคุ้มค่า ในช่วงตลาดหมี ที่กำไรจากการขุดต่ำ การลดต้นทุนไฟฟ้าคือทางรอดหลัก
เครื่องขุด Bitcoin (ASIC) รุ่นไหน ที่เหมาะกับสาย Tuning Power
-
Antminer รองรับ Custom Firmware เช่น Braiins OS ที่เป็นยอดนิยมในการ Tuning Power
-
WhatsMiner M30-M60s Series ขึ้นไป ใช้โปรแกรม WhatsMinerTool เพื่อทำการ Tuning Power ได้โดยตรงไม่จำเป็นต้อง Custom Firmware
สรุป การเป็น Home Miner ที่ยั่งยืนไม่ได้ขึ้นกับว่าเครื่องขุดแรงแค่ไหน แต่ขึ้นกับว่า “จ่ายค่าไฟแล้วเหลือกำไรหรือไม่ หรือ จ่ายค่าไฟแล้วคุ้มค้ารายได้ Bitcoin จากการขุดจำนวนที่ได้รับมากขึ้นหรือไม่” การเลือกเครื่องขุดสำหรับสาย Tuning Power จึงเป็นทางเลือกที่ตอบโจทย์ผู้ที่ต้องการประสิทธิภาพสูงในต้นทุนที่ควบคุมได้โดยเฉพาะในยุคที่ตลาดผันผวน และ ค่าไฟฟ้าคือศัตรูตัวจริงของนักขุด
-
 @ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03
@ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:59:23
@ 04c915da:3dfbecc9
2025-05-16 17:59:23Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ 554ab6fe:c6cbc27e
2025-05-20 15:51:33
@ 554ab6fe:c6cbc27e
2025-05-20 15:51:33Introduction
It is becoming increasingly evident that sunlight is an essential nutrient for the body. To be more precise, the various wavelengths coming from the sun provide different benefits to the body, and each play a vital role in human health. Even more so, they work in concert with one another, as one wavelength may help reduce the potentially harmful effects of another. Benefits are maximized and harm reduced when we are exposed to the full breadth of this rainbow. This article will attempt to shed light on these various benefits and synergies.
To put this discussion into context, it is important to consider the overall health benefits of sunlight exposure. In a Swedish study that followed 29,000 women over 20 years, it was found that the mortality rate was doubled in those who avoided sun exposure when compared to those that didn’t (Lindqvist et al. 2016). Women who avoided the sun were twice as likely to die, primarily from cardiovascular disease, and there was no difference between death from malignant melanoma between the two groups (Lindqvist et al. 2016).
To understand why sunlight is so beneficial to health, it is important to make clear the diverse range of wavelengths that come from the sun. We typically think of the sun as a provider of both visible light and warmth. However, the spectrum of light visible to the human eye is a narrow band of the wavelengths actually emitted by the sun.


As wavelengths become shorter, visible light becomes more blue. Beyond the visible spectrum on the blue end, we arrive at ultraviolet (UV) light. On the other end of the spectrum are the longer red wavelengths. Outside of the visible window on the red side is infrared (IR) light, which provides heat. For helpful context, consider how shorter wavelengths have a harder time penetrating our atmosphere. So, the skies of dawn and dusk are predominately filled with red and near-infrared (NIR) light, while the middle of the day contains more blue and UV light. The bulk of wavelengths from the sun throughout the day are on the NIR end. The entire spectrum of visible and non-visible light between UV and IR plays critical roles in human health, especially towards mitochondrial health and metabolism. To summarize these benefits and provide a general overview for the following article, the benefits are as follows:
- UV – aids in the production of vitamin D and melanin, but also causes DNA damage
- Vitamin D improves immune system function and can repair DNA damage
- Melanin stores electrons for use within mitochondria
- Blue – involved in our circadian rhythm as the absence of blue light triggers the production of melatonin, an important antioxidant.
- Near-infrared (NIR) – improves mitochondria function and energy production while also protecting us from the harms of blue and UV light.
Ultraviolet Light
Let’s begin with a discussion around the widely misunderstood light of UV. UV is often viewed as a dangerous form of light, given that it can cause DNA damage and lead to cancer. While true, this myopic point of view ignores the crucial benefits of UV light. UV light produces vitamin D, which counteracts the DNA damage caused by UV while providing many other benefits. Additionally, UV light triggers the production of melanin, which aids in mitochondrial function. Like all physiological processes in the body that are vital to survival, there is a release of POMC-derived endorphins when skin comes into contact with UV light (Fell et al. 2014). Any person likely reading this article can agree that sitting under the sun simply feels amazing. We are drawn to it in a deeply meaningful sense.
Vitamin D is one of the most important chemicals regarding health, and it is poorly named. The term ‘vitamin’ refers to a compound that is important for health but cannot be adequately made within the body and must be retrieved externally. Peoples of the Northern and Southern hemisphere who are exposed to less UV light during winter would, for example, historically retrieve their vitamin D from foods such as oily fish, seal blubber, whale blubber, and polar bear liver (Wacker and Holick 2013). In a similar way, vitamin D was given its name 100 years ago when it was found that cod-liver oil was capable of curing rickets, when it was found that the so-called vitamin could promote calcium deposition in bones (McCollum et al. 1922). It was only until much later, in 1981, when scientists discovered that human skin could also synthesize vitamin D (M. F. Holick 1981). A majority of human vitamin D is produced by the skin when exposed to UVB (280 – 315 nm), while a minor amount is gained through food (Prietl et al. 2013; Wacker and Holick 2013). Most cells and organs in the human body have vitamin D receptors and many organs also have the ability to produce it, this speaks to the incredibly important nature of this compound towards our health (Prietl et al. 2013; Wacker and Holick 2013). Vitamin D deficiency has been associated with various types of cancer, autoimmune disorders, type 1 diabetes mellitus, multiple sclerosis (MS), cardiovascular disease, and even schizophrenia (Michael F. Holick 2007; Wacker and Holick 2013). Multiple studies have also found that vitamin D deficiency increases all-cause mortality (Garland et al. 2014; Yang et al. 2011; Chowdhury et al. 2014).
Though the historical benefits to vitamin D were attributed mainly to bone health, it is far more important. Vitamin D plays a critical role in protecting against invasive pathogens, reducing autoimmunity, and maintaining overall health (Wimalawansa 2023). Regarding immunity, one way it does this is by causing a shift away from proinflammatory responses to one more centered around T cell activation (Prietl et al. 2013). Vitamin D has therefore been shown to benefit other disorders that are related to immunity, such as a study that found vitamin D supplementation during pregnancy reduced asthmatic symptoms in children (Litonjua et al. 2016). That being said, it is important to highlight how there is no substitution for natural sunlight as a means of getting vitamin D. Naturally produced vitamin D from the skin lasts 2-3 times longer in the body (Wacker and Holick 2013). This is one of many likely reasons why the natural avenue should always be preferred over the supplemental. A similar line of reasoning follows in methods of getting UV light, as natural sun exposure leads to a decrease of all-cause mortality while the use of artificial tanning beds has been shown to increase all-cause and cancer mortality (Yang et al. 2011). More on why this likely occurs later.
Beyond vitamin D’s benefits to the immune system, it is important to focus on the compound’s role in mitochondrial health. In a previous article I wrote titled “Sunlight and Health”, I delve deeper into the importance of mitochondria and the science of how they work. In simplicity, imagine how all life on earth centers around energy. The sun provides energy to the earth, and the plethora of life on earth harness and facilitate the flow of that energy. Plants and animals share a symbiotic relationship within this system. Plants, through photosynthesis, take in sunlight, CO2, and water and create a glucose precursor and oxygen. This occurs within the chloroplast of plant cells. Within human cells, we have mitochondria. Our mitochondria, in turn, take in oxygen and glucose and produce CO2, water, and energy for our bodies in the form of ATP. What the plant breathes out, we breathe in, and vice versa. Mitochondria are central to all animal life on earth, and the ATP produced is central to all physiologic function. If your mitochondria are unhealthy, you are unhealthy and will experience disease.
Vitamin D plays a role in mitochondrial health at a DNA level. Our cells have DNA, which we inherited from our mother and father. On top of that, the mitochondria within our cells have their own set of DNA (mtDNA). Our mitochondria come from our mother’s egg, and therefore our mtDNA always is inherited from our mother. UV light can cause damage to both our DNA and mtDNA (Birch-Machin, Russell, and Latimer 2013). This is what gives UV light the ability to cause cancer. Additionally, damage to the mtDNA within our mitochondria can lead to mitochondrial dysfunction. The more poorly our mitochondria function, the less energy we produce for our cells, and the less healthy our cells become. There is research being developed that suggests the role of vitamin D is to counterbalance this danger by regulating gene transcription and reducing mtDNA damage. A mouse study conducted in 2011, for example, found that different shapes of vitamin D reduce the development of tumors in mice following UV exposure (Dixon et al. 2011). It is not unlike nature to create a system of checks and balances, to ensure that the damaging effects of UV light are counterbalanced by a compound produced by the body when exposure to that same light.
While vitamin D may be important for mitochondrial health by protecting against mtDNA damage, melanin potentially plays a much larger role. Melanin is the pigment in our skin that make us darker. Not only is the diversity in skin tones across humans due to variations in melanin content, but a tan is also the creation of more melanin. To be more specific, the skin’s exposure to UVA (315-400nm) leads to the creation of melanin (Wicks et al. 2011). The most obvious benefit to the production of melanin, which most people could appreciate, is that the darker or tanner our skin is, the less damage we will receive from UV light. In this way, melanin shares a similar responsibility to vitamin D, where both are protecting the body against the very thing that forms them. Even more crucially however, melanin acts as a battery for the mitochondria.
During cellular respiration, where mitochondria turn oxygen and glucose into energy, electrons are stripped from the glucose for use. In other words, what our mitochondria really need are oxygen and electrons, and the glucose is simply a means to an end. If the mitochondria are the engine, then the electrons are the fuel (assuming you are still breathing). Due to its chemical structure, melanin is a natural reversible oxidation-reduction system (Figge 1939). In other words, it can both store and release electrons. Melanin is therefore a kind of battery, retrieving electrons from various sources, and storing them for future use in our mitochondria as a substitute for food. When stated this way, and considering how food is important because both fats and carbohydrates fuel the body by providing electrons to our mitochondria, one can imagine how vitally important melanin is. Melanin is central towards the availability of electrons for use in our body to produce the energy to live. Without adequate melanin, your mitochondria will starve for fuel and not provide your body with the energy it needs to thrive.
Blue Light
To contextualize the role blue light plays in human health, it is important to revisit an important byproduct of cellular respiration within mitochondria. When mitochondria turn electrons and oxygen into energy, there is a byproduct formed known as reactive oxygen species (ROS). ROS play important roles in the body, but in excess they can cause DNA damage and disrupt various cellular processes. For example, UV light causes cancer due to the ROS generated, and studies have found that blue light does the same in both the skin and eyes (Nakashima, Ohta, and Wolf 2017; Abdouh et al. 2024). This research suggests that excess blue light or blue light in isolation can damage the eyes and cause harm like UV light.
Blue and UV light are predominant during the middle of the day. Though both may cause oxidative stress on the body, the body simultaneously counteracts this damage through melatonin. Think of melatonin as the junk remover for mitochondria. Throughout the day mitochondria produce energy, and ROS is formed. During our nighttime sleep, melatonin plays an important role as an antioxidant and removes the excess ROS (Leon et al. 2004).
The relationship between blue light and melatonin is important. During the day, when blue light is present, our body suppresses the production of melatonin (West et al. 2011). When the sun sets and there is no longer a heavy presence of blue light, our body begins to produce melatonin for sleep. This is a central function for how our body gets tired at night and gets ready for sleep. This is also why artificial light at night, from our modern technology, is harmful to human health because it tricks the body into the continual suppression of melatonin production. Without proper melatonin production, our cells buildup too much ROS and this can cause mitochondrial dysfunction and other sleep related issues.
Beyond the importance of getting good sleep and producing melatonin to remove excess ROS from our cells, the existence of artificial light and excess blue light is problematic during the day as well. As stated previously, blue light causes ROS buildup in both the skin and eyes (Nakashima, Ohta, and Wolf 2017; Abdouh et al. 2024). As with most harms from sunlight, our body has adapted with a backup plan. During the day, when blue and UV light is present, there is simultaneous exposure to NIR light (650-1200nm). Recent research suggests that NIR also counterbalances the harm of blue light by increasing melatonin synthesis in the mitochondria (Tan et al. 2023). This highlights the importance of receiving the full spectrum of light from the sun, as one wavelength counterbalances the damages of the other.
Near-Infrared Light
While indoor living has been commonplace for humans across generations, and modern technology has over saturated our bodies with blue light, some recent changes to our technology have made things worse. Incandescent light bulbs emit NIR light, this is why they got warm. However, LED lights do not emit NIR light. Therefore, where people of past generations were potentially exposed to a lot of artificial light at night, this was counterbalanced by the NIR emitted by those same lightbulbs. Now, modern humans use LEDs and spend 93% of our time indoors with zero exposure to NIR, which is 90% of the light emitted by the sun (Tan et al. 2023).
Not only does NIR light protect our bodies from the damaging consequences of blue light, but it similarly protects us against UV light. As stated previously, NIR may result in the production of melatonin within mitochondria during the day, helping protect against the ROS buildup and mtDNA damage. Additionally, research has also found that NIR light protects from UV light in other ways. For example, a study in 2008 found that pretreating skin with NIR light (660nm) prevented sunburns (Barolet and Boucher 2008). Another study found that red and NIR light (620-690nm) altered gene expression and upregulated DNA repair (Kim et al. 2019). Again, this highlights the theme that the body has produced the means to protect itself from the harms of the sun via other rays emitted. However, the protection from harmful rays is best achieved when exposed to the full spectrum of light wavelengths as they change throughout the day. The light of dawn and dusk is predominately red and NIR. Therefore, this research suggests that being exposed to morning light will protect the body from the potentially cancer-causing effects of the UV light later in the day. A human being who lived outside would naturally be exposed to this spectrum of light every day. However, modern humans may be inside in the morning, go to the beach during the middle of the day, and get sunburned because they do not properly receive the full spectrum of light as nature intended every day.
Lastly, it is important to explore the ways NIR improves mitochondrial function. If electrons are the fuel source for this engine, and melatonin is the junk removal, then NIR is the lubricant. NIR improves the energy output of mitochondria, and there are various hypotheses for how this occurs. One hypothesis is that NIR boosts the functionality of cytochrome c oxidase, one of the chromophores used in the electron transport chain (ETC) of cellular respiration within mitochondria (De Freitas and Hamblin 2016). Another involves NIR light’s ability to modify the viscosity of water which increases the efficiency of the final step in the ETC, the ATP synthase (Sommer, Haddad, and Fecht 2015). ATP synthase can be thought of as a kind of pump that produces ATP, in this way NIR can be thought of almost literally as a lubricant for this pump.
Summary
In summary, the research involving how sunlight affects mitochondrial health highlights the importance of the full spectrum of wavelengths, each of which plays a vital role in human health throughout the day. Having exposure to one, without the other, can lead to imbalances and mitochondrial disease. The red and NIR light in the morning helps our mitochondria produce more energy throughout the day, while also preparing our bodies for the beneficial yet dangerous wavelengths to come. In the middle of the day, we receive much more UV and blue light, which help us produce vitamin D and melanin, both central to health and wellness. Once the sun sets, and blue light is absent, we produce melatonin for sleep. During our sleep, the melatonin removes the dangerous byproducts of our energy-producing day, protecting us from disease and preparing us for the following day. Mitochondria are central to human health and life on earth, and the rays from the sun are central to mitochondrial health.
Respecting nature and its cycles is vital for us humans who are increasingly immersing ourselves in a world dominated by technology. Our ancestors did not have to reconcile with these ideas, because life forced these exposures upon them. If we wish to maintain health in our modern world, we must be able to find balance. Even though some might think they can escape into the virtual world, our bodies will always and forever be connected and reliant upon the natural one.
References
Abdouh, Mohamed, Yunxi Chen, Alicia Goyeneche, and Miguel N. Burnier. 2024. “Blue Light-Induced Mitochondrial Oxidative Damage Underlay Retinal Pigment Epithelial Cell Apoptosis.” International Journal of Molecular Sciences 25 (23): 12619.
Barolet, Daniel, and Annie Boucher. 2008. “LED Photoprevention: Reduced MED Response Following Multiple LED Exposures.” Lasers in Surgery and Medicine 40 (2): 106–12.
Birch-Machin, M. A., E. V. Russell, and J. A. Latimer. 2013. “Mitochondrial DNA Damage as a Biomarker for Ultraviolet Radiation Exposure and Oxidative Stress.” The British Journal of Dermatology 169 (s2): 9–14.
Chowdhury, Rajiv, Setor Kunutsor, Anna Vitezova, Clare Oliver-Williams, Susmita Chowdhury, Jessica C. Kiefte-de-Jong, Hassan Khan, et al. 2014. “Vitamin D and Risk of Cause Specific Death: Systematic Review and Meta-Analysis of Observational Cohort and Randomised Intervention Studies.” BMJ (Clinical Research Ed.) 348 (apr01 2): g1903.
De Freitas, Lucas Freitas, and Michael R. Hamblin. 2016. “Proposed Mechanisms of Photobiomodulation or Low-Level Light Therapy.” IEEE Journal of Selected Topics in Quantum Electronics: A Publication of the IEEE Lasers and Electro-Optics Society 22 (3): 348–64.
Dixon, Katie M., Anthony W. Norman, Vanessa B. Sequeira, Ritu Mohan, Mark S. Rybchyn, Vivienne E. Reeve, Gary M. Halliday, and Rebecca S. Mason. 2011. “1α,25(OH)₂-Vitamin D and a Nongenomic Vitamin D Analogue Inhibit Ultraviolet Radiation-Induced Skin Carcinogenesis.” Cancer Prevention Research (Philadelphia, Pa.) 4 (9): 1485–94.
Fell, Gillian L., Kathleen C. Robinson, Jianren Mao, Clifford J. Woolf, and David E. Fisher. 2014. “Skin β-Endorphin Mediates Addiction to UV Light.” Cell 157 (7): 1527–34.
Figge, Frank H. J. 1939. “Melanin: A Natural Reversible Oxidation-Reduction System and Indicator.” Experimental Biology and Medicine (Maywood, N.J.) 41 (1): 127.
Garland, Cedric F., June Jiwon Kim, Sharif Burgette Mohr, Edward Doerr Gorham, William B. Grant, Edward L. Giovannucci, Leo Baggerly, et al. 2014. “Meta-Analysis of All-Cause Mortality According to Serum 25-Hydroxyvitamin D.” American Journal of Public Health 104 (8): e43-50.
Holick, M. F. 1981. “The Cutaneous Photosynthesis of Previtamin D3: A Unique Photoendocrine System.” The Journal of Investigative Dermatology 77 (1): 51–58.
Holick, Michael F. 2007. “Vitamin D Deficiency.” The New England Journal of Medicine 357 (3): 266–81.
Kim, Hyun Soo, Yeo Jin Kim, Su Ji Kim, Doo Seok Kang, Tae Ryong Lee, Dong Wook Shin, Hyoung-June Kim, and Young Rok Seo. 2019. “Transcriptomic Analysis of Human Dermal Fibroblast Cells Reveals Potential Mechanisms Underlying the Protective Effects of Visible Red Light against Damage from Ultraviolet B Light.” Journal of Dermatological Science 94 (2): 276–83.
Leon, Josefa, Dario Acuña-Castroviejo, Rosa M. Sainz, Juan C. Mayo, Dun Xian Tan, and Russel J. Reiter. 2004. “Melatonin and Mitochondrial Function.” Life Sciences. Elsevier Inc. https://doi.org/10.1016/j.lfs.2004.03.003.
Lindqvist, P. G., E. Epstein, K. Nielsen, M. Landin-Olsson, C. Ingvar, and H. Olsson. 2016. “Avoidance of Sun Exposure as a Risk Factor for Major Causes of Death: A Competing Risk Analysis of the Melanoma in Southern Sweden Cohort.” Journal of Internal Medicine 280 (4): 375–87.
Litonjua, Augusto A., Vincent J. Carey, Nancy Laranjo, Benjamin J. Harshfield, Thomas F. McElrath, George T. O’Connor, Megan Sandel, et al. 2016. “Effect of Prenatal Supplementation with Vitamin D on Asthma or Recurrent Wheezing in Offspring by Age 3 Years: The VDAART Randomized Clinical Trial.” JAMA: The Journal of the American Medical Association 315 (4): 362–70.
McCollum, E. V., Nina Simmonds, J. Ernestine Becker, and P. G. Shipley. 1922. “Studies on Experimental Rickets.” The Journal of Biological Chemistry 53 (2): 293–312.
Nakashima, Yuya, Shigeo Ohta, and Alexander M. Wolf. 2017. “Blue Light-Induced Oxidative Stress in Live Skin.” Free Radical Biology & Medicine 108 (July): 300–310.
Prietl, Barbara, Gerlies Treiber, Thomas R. Pieber, and Karin Amrein. 2013. “Vitamin D and Immune Function.” Nutrients 5 (7): 2502–21.
Sommer, Andrei P., Mike Kh Haddad, and Hans Jörg Fecht. 2015. “Light Effect on Water Viscosity: Implication for ATP Biosynthesis.” Scientific Reports 5 (July). https://doi.org/10.1038/srep12029.
Tan, Dun-Xian, Russel J. Reiter, Scott Zimmerman, and Ruediger Hardeland. 2023. “Melatonin: Both a Messenger of Darkness and a Participant in the Cellular Actions of Non-Visible Solar Radiation of near Infrared Light.” Biology 12 (1): 89.
Wacker, Matthias, and Michael F. Holick. 2013. “Sunlight and Vitamin D: A Global Perspective for Health: A Global Perspective for Health.” Dermato-Endocrinology 5 (1): 51–108.
West, Kathleen E., Michael R. Jablonski, Benjamin Warfield, Kate S. Cecil, Mary James, Melissa A. Ayers, James Maida, et al. 2011. “Blue Light from Light-Emitting Diodes Elicits a Dose-Dependent Suppression of Melatonin in Humans.” Journal of Applied Physiology (Bethesda, Md.: 1985) 110 (3): 619–26.
Wicks, Nadine L., Jason W. Chan, Julia A. Najera, Jonathan M. Ciriello, and Elena Oancea. 2011. “UVA Phototransduction Drives Early Melanin Synthesis in Human Melanocytes.” Current Biology: CB 21 (22): 1906.
Wimalawansa, Sunil J. 2023. “Infections and Autoimmunity-the Immune System and Vitamin D: A Systematic Review.” Nutrients 15 (17): 3842.
Yang, Ling, Marie Lof, Marit Bragelien Veierød, Sven Sandin, Hans-Olov Adami, and Elisabete Weiderpass. 2011. “Ultraviolet Exposure and Mortality among Women in Sweden.” Cancer Epidemiology, Biomarkers & Prevention: A Publication of the American Association for Cancer Research, Cosponsored by the American Society of Preventive Oncology 20 (4): 683–90.
- UV – aids in the production of vitamin D and melanin, but also causes DNA damage
-
 @ a5ee4475:2ca75401
2025-05-15 14:44:45
@ a5ee4475:2ca75401
2025-05-15 14:44:45lista #descentralismo #compilado #portugues
*Algumas destas listas ainda estão sendo trocadas, portanto as versões mais recentes delas só estão visíveis no Amethyst por causa da ferramenta de edição.
Clients do Nostr e Outras Coisas
nostr:naddr1qq245dz5tqe8w46swpphgmr4f3047s6629t45qg4waehxw309aex2mrp0yhxgctdw4eju6t09upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4guxde6sl
Modelos de IA e Ferramentas
nostr:naddr1qq24xwtyt9v5wjzefe6523j32dy5ga65gagkjqgswaehxw309ahx7um5wghx6mmd9upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4guk62czu
Iniciativas de Bitcoin
nostr:naddr1qvzqqqr4gupzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqq2nvmn5va9x2nrxfd2k5smyf3ux7vesd9znyqxygt4
Profissionais Brasileiros no Nostr
nostr:naddr1qq24qmnkwe6y67zlxgc4sumrxpxxce3kf9fn2qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7q3q5hhygatg5gmjyfkkguqn54f9r6k8m5m6ksyqffgjrf3uut982sqsxpqqqp65wp8uedu
Comunidades em Português no Nostr
nostr:naddr1qq2hwcejv4ykgdf3v9gxykrxfdqk753jxcc4gqg4waehxw309aex2mrp0yhxgctdw4eju6t09upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4gu455fm3
Grupos em Português no Nostr
nostr:nevent1qqs98kldepjmlxngupsyth40n0h5lw7z5ut5w4scvh27alc0w86tevcpzpmhxue69uhkummnw3ezumt0d5hsygy7fff8g6l23gp5uqtuyqwkqvucx6mhe7r9h7v6wyzzj0v6lrztcspsgqqqqqqs3ndneh
Jogos de Código Aberto
Open Source Games nostr:naddr1qvzqqqr4gupzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqq2kvwp3v4hhvk2sw3j5sm6h23g5wkz5ddzhz8x40v0
Itens Úteis com Esquemas Disponíveis
nostr:naddr1qqgrqvp5vd3kycejxask2efcv4jr2qgswaehxw309ahx7um5wghx6mmd9upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4guc43v6c
Formatação de Texto em Markdown
(Amethyst, Yakihone e outros) nostr:naddr1qvzqqqr4gupzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqq2454m8dfzn26z4f34kvu6fw4rysnrjxfm42wfpe90
Outros Links
nostr:nevent1qqsrm6ywny5r7ajakpppp0lt525n0s33x6tyn6pz0n8ws8k2tqpqracpzpmhxue69uhkummnw3ezumt0d5hsygp6e5ns0nv3dun430jky25y4pku6ylz68rz6zs7khv29q6rj5peespsgqqqqqqsmfwa78
-
 @ 088436cd:9d2646cc
2025-05-01 21:01:55
@ 088436cd:9d2646cc
2025-05-01 21:01:55The arrival of the coronavirus brought not only illness and death but also fear and panic. In such an environment of uncertainty, people have naturally stocked up on necessities, not knowing when things will return to normal.
Retail shelves have been cleared out, and even online suppliers like Amazon and Walmart are out of stock for some items. Independent sellers on these e-commerce platforms have had to fill the gap. With the huge increase in demand, they have found that their inventory has skyrocketed in value.
Many in need of these items (e.g. toilet paper, hand sanitizer and masks) balk at the new prices. They feel they are being taken advantage of in a time of need and call for intervention by the government to lower prices. The government has heeded that call, labeling the independent sellers as "price gougers" and threatening sanctions if they don't lower their prices. Amazon has suspended seller accounts and law enforcement at all levels have threatened to prosecute. Prices have dropped as a result and at first glance this seems like a victory for fair play. But, we will have to dig deeper to understand the unseen consequences of this intervention.
We must look at the economics of the situation, how supply and demand result in a price and how that price acts as a signal that goes out to everyone, informing them of underlying conditions in the economy and helping coordinate their actions.
It all started with a rise in demand. Given a fixed supply (e.g., the limited stock on shelves and in warehouses), an increase in demand inevitably leads to higher prices. Most people are familiar with this phenomenon, such as paying more for airline tickets during holidays or surge pricing for rides.
Higher prices discourage less critical uses of scarce resources. For example, you might not pay $1,000 for a plane ticket to visit your aunt if you can get one for $100 the following week, but someone else might pay that price to visit a dying relative. They value that plane seat more than you.
*** During the crisis, demand surged and their shelves emptied even though
However, retail outlets have not raised prices. They have kept them low, so the low-value uses of things like toilet paper, masks and hand sanitizer has continued. Often, this "use" just takes the form of hoarding. At everyday low prices, it makes sense to buy hundreds of rolls and bottles. You know you will use them eventually, so why not stock up? And, with all those extra supplies in the closet and basement, you don't need to change your behavior much. You don't have to ration your use.
At the low prices, these scarce resources got bought up faster and faster until there was simply none left. The reality of the situation became painfully clear to those who didn't panic and got to the store late: You have no toilet paper and you're not going to any time soon.
However, if prices had been allowed to rise, a number of effects would have taken place that would have coordinated the behavior of everyone so that valuable resources would not have been wasted or hoarded, and everyone could have had access to what they needed.
On the demand side, if prices had been allowed to rise, people would have begun to self-ration. You might leave those extra plies on the roll next time if you know they will cost ten times as much to replace. Or, you might choose to clean up a spill with a rag rather than disposable tissue. Most importantly, you won't hoard as much. That 50th bottle of hand sanitizer might just not be worth it at the new, high price. You'll leave it on the shelf for someone else who may have none.
On the supply side, higher prices would have incentivized people to offer up more of their stockpiles for sale. If you have a pallet full of toilet paper in your basement and all of the sudden they are worth $15 per roll, you might just list a few online. But, if it is illegal to do so, you probably won't.
Imagine you run a business installing insulation and have a few thousand respirator masks on hand for your employees. During a pandemic, it is much more important that people breathe filtered air than that insulation get installed, and that fact is reflected in higher prices. You will sell your extra masks at the higher price rather than store them for future insulation jobs, and the scarce resource will be put to its most important use.
Producers of hand sanitizer would go into overdrive if prices were allowed to rise. They would pay their employees overtime, hire new ones, and pay a premium for their supplies, making sure their raw materials don't go to less important uses.
These kinds of coordinated actions all across the economy would be impossible without real prices to guide them. How do you know if it makes sense to spend an extra $10k bringing a thousand masks to market unless you know you can get more than $10 per mask? If the price is kept artificially low, you simply can't do it. The money just isn't there.
These are the immediate effects of a price change, but incredibly, price changes also coordinate people's actions across space and time.
Across space, there are different supply and demand conditions in different places, and thus prices are not uniform. We know some places are real "hot spots" for the virus, while others are mostly unaffected. High demand in the hot spots leads to higher prices there, which attracts more of the resource to those areas. Boxes and boxes of essential items would pour in where they are needed most from where they are needed least, but only if prices were allowed to adjust freely.
This would be accomplished by individuals and businesses buying low in the unaffected areas, selling high in the hot spots and subtracting their labor and transportation costs from the difference. Producers of new supply would know exactly where it is most needed and ship to the high-demand, high-price areas first. The effect of these actions is to increase prices in the low demand areas and reduce them in the high demand areas. People in the low demand areas will start to self-ration more, reflecting the reality of their neighbors, and people in the hotspots will get some relief.
However, by artificially suppressing prices in the hot spot, people there will simply buy up the available supply and run out, and it will be cost prohibitive to bring in new supply from low-demand areas.
Prices coordinate economic actions across time as well. Just as entrepreneurs and businesses can profit by transporting scarce necessities from low-demand to high-demand areas, they can also profit by buying in low-demand times and storing their merchandise for when it is needed most.
Just as allowing prices to freely adjust in one area relative to another will send all the right signals for the optimal use of a scarce resource, allowing prices to freely adjust over time will do the same.
When an entrepreneur buys up resources during low-demand times in anticipation of a crisis, she restricts supply ahead of the crisis, which leads to a price increase. She effectively bids up the price. The change in price affects consumers and producers in all the ways mentioned above. Consumers self-ration more, and producers bring more of the resource to market.
Our entrepreneur has done a truly incredible thing. She has predicted the future, and by so doing has caused every individual in the economy to prepare for a shortage they don't even know is coming! And, by discouraging consumption and encouraging production ahead of time, she blunts the impact the crisis will have. There will be more of the resource to go around when it is needed most.
On top of this, our entrepreneur still has her stockpile she saved back when everyone else was blithely using it up. She can now further mitigate the damage of the crisis by selling her stock during the worst of it, when people are most desperate for relief. She will know when this is because the price will tell her, but only if it is allowed to adjust freely. When the price is at its highest is when people need the resource the most, and those willing to pay will not waste it or hoard it. They will put it to its highest valued use.
The economy is like a big bus we are all riding in, going down a road with many twists and turns. Just as it is difficult to see into the future, it is difficult to see out the bus windows at the road ahead.
On the dashboard, we don't have a speedometer or fuel gauge. Instead we have all the prices for everything in the economy. Prices are what tell us the condition of the bus and the road. They tell us everything. Without them, we are blind.
Good times are a smooth road. Consumer prices and interest rates are low, investment returns are steady. We hit the gas and go fast. But, the road is not always straight and smooth. Sometimes there are sharp turns and rough patches. Successful entrepreneurs are the ones who can see what is coming better than everyone else. They are our navigators.
When they buy up scarce resources ahead of a crisis, they are hitting the brakes and slowing us down. When they divert resources from one area to another, they are steering us onto a smoother path. By their actions in the market, they adjust the prices on our dashboard to reflect the conditions of the road ahead, so we can prepare for, navigate and get through the inevitable difficulties we will face.
Interfering with the dashboard by imposing price floors or price caps doesn't change the conditions of the road (the number of toilet paper rolls in existence hasn't changed). All it does is distort our perception of those conditions. We think the road is still smooth--our heavy foot stomping the gas--as we crash onto a rocky dirt road at 80 miles per hour (empty shelves at the store for weeks on end).
Supply, demand and prices are laws of nature. All of this is just how things work. It isn't right or wrong in a moral sense. Price caps lead to waste, shortages and hoarding as surely as water flows downhill. The opposite--allowing prices to adjust freely--leads to conservation of scarce resources and their being put to their highest valued use. And yes, it leads to profits for the entrepreneurs who were able to correctly predict future conditions, and losses for those who weren't.
Is it fair that they should collect these profits? On the one hand, anyone could have stocked up on toilet paper, hand sanitizer and face masks at any time before the crisis, so we all had a fair chance to get the supplies cheaply. On the other hand, it just feels wrong that some should profit so much at a time when there is so much need.
Our instinct in the moment is to see the entrepreneur as a villain, greedy "price gouger". But we don't see the long chain of economic consequences the led to the situation we feel is unfair.
If it weren't for anti-price-gouging laws, the major retailers would have raised their prices long before the crisis became acute. When they saw demand outstrip supply, they would have raised prices, not by 100 fold, but gradually and long before anyone knew how serious things would have become. Late comers would have had to pay more, but at least there would be something left on the shelf.
As an entrepreneur, why take risks trying to anticipate the future if you can't reap the reward when you are right? Instead of letting instead of letting entrepreneurs--our navigators--guide us, we are punishing and vilifying them, trying to force prices to reflect a reality that simply doesn't exist.
In a crisis, more than any other time, prices must be allowed to fluctuate. To do otherwise is to blind ourselves at a time when danger and uncertainty abound. It is economic suicide.
In a crisis, there is great need, and the way to meet that need is not by pretending it's not there, by forcing prices to reflect a world where there isn't need. They way to meet the need is the same it has always been, through charity.
If the people in government want to help, the best way for the to do so is to be charitable and reduce their taxes and fees as much as possible, ideally to zero in a time of crisis. Amazon, for example, could instantly reduce the price of all crisis related necessities by 20% if they waived their fee. This would allow for more uses by more people of these scarce supplies as hoarders release their stockpiles on to the market, knowing they can get 20% more for their stock. Governments could reduce or eliminate their tax burden on high-demand, crisis-related items and all the factors that go into their production, with the same effect: a reduction in prices and expansion of supply. All of us, including the successful entrepreneurs and the wealthy for whom high prices are not a great burden, could donate to relief efforts.
These ideas are not new or untested. This is core micro economics. It has been taught for hundreds of years in universities the world over. The fact that every crisis that comes along stirs up ire against entrepreneurs indicates not that the economics is wrong, but that we have a strong visceral reaction against what we perceive to be unfairness. This is as it should be. Unfairness is wrong and the anger it stirs in us should compel us to right the wrong. Our anger itself isn't wrong, it's just misplaced.
Entrepreneurs didn't cause the prices to rise. Our reaction to a virus did that. We saw a serious threat and an uncertain future and followed our natural impulse to hoard. Because prices at major retail suppliers didn't rise, that impulse ran rampant and we cleared the shelves until there was nothing left. We ran the bus right off the road and them blamed the entrepreneurs for showing us the reality of our situation, for shaking us out of the fantasy of low prices.
All of this is not to say that entrepreneurs are high-minded public servants. They are just doing their job. Staking your money on an uncertain future is a risky business. There are big risks and big rewards. Most entrepreneurs just scrape by or lose their capital in failed ventures.
However, the ones that get it right must be allowed to keep their profits, or else no one will try and we'll all be driving blind. We need our navigators. It doesn't even matter if they know all the positive effects they are having on the rest of us and the economy as a whole. So long as they are buying low and selling high--so long as they are doing their job--they will be guiding the rest of us through the good times and the bad, down the open road and through the rough spots.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ 04c915da:3dfbecc9
2025-05-20 15:50:48
@ 04c915da:3dfbecc9
2025-05-20 15:50:48For years American bitcoin miners have argued for more efficient and free energy markets. It benefits everyone if our energy infrastructure is as efficient and robust as possible. Unfortunately, broken incentives have led to increased regulation throughout the sector, incentivizing less efficient energy sources such as solar and wind at the detriment of more efficient alternatives.
The result has been less reliable energy infrastructure for all Americans and increased energy costs across the board. This naturally has a direct impact on bitcoin miners: increased energy costs make them less competitive globally.
Bitcoin mining represents a global energy market that does not require permission to participate. Anyone can plug a mining computer into power and internet to get paid the current dynamic market price for their work in bitcoin. Using cellphone or satellite internet, these mines can be located anywhere in the world, sourcing the cheapest power available.
Absent of regulation, bitcoin mining naturally incentivizes the build out of highly efficient and robust energy infrastructure. Unfortunately that world does not exist and burdensome regulations remain the biggest threat for US based mining businesses. Jurisdictional arbitrage gives miners the option of moving to a friendlier country but that naturally comes with its own costs.
Enter AI. With the rapid development and release of AI tools comes the requirement of running massive datacenters for their models. Major tech companies are scrambling to secure machines, rack space, and cheap energy to run full suites of AI enabled tools and services. The most valuable and powerful tech companies in America have stumbled into an accidental alliance with bitcoin miners: THE NEED FOR CHEAP AND RELIABLE ENERGY.
Our government is corrupt. Money talks. These companies will push for energy freedom and it will greatly benefit us all.
-
 @ 4ba8e86d:89d32de4
2025-04-21 02:13:56
@ 4ba8e86d:89d32de4
2025-04-21 02:13:56Tutorial feito por nostr:nostr:npub1rc56x0ek0dd303eph523g3chm0wmrs5wdk6vs0ehd0m5fn8t7y4sqra3tk poste original abaixo:
Parte 1 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/263585/tutorial-debloat-de-celulares-android-via-adb-parte-1
Parte 2 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/index.php/263586/tutorial-debloat-de-celulares-android-via-adb-parte-2
Quando o assunto é privacidade em celulares, uma das medidas comumente mencionadas é a remoção de bloatwares do dispositivo, também chamado de debloat. O meio mais eficiente para isso sem dúvidas é a troca de sistema operacional. Custom Rom’s como LineageOS, GrapheneOS, Iodé, CalyxOS, etc, já são bastante enxutos nesse quesito, principalmente quanto não é instalado os G-Apps com o sistema. No entanto, essa prática pode acabar resultando em problemas indesejados como a perca de funções do dispositivo, e até mesmo incompatibilidade com apps bancários, tornando este método mais atrativo para quem possui mais de um dispositivo e separando um apenas para privacidade. Pensando nisso, pessoas que possuem apenas um único dispositivo móvel, que são necessitadas desses apps ou funções, mas, ao mesmo tempo, tem essa visão em prol da privacidade, buscam por um meio-termo entre manter a Stock rom, e não ter seus dados coletados por esses bloatwares. Felizmente, a remoção de bloatwares é possível e pode ser realizada via root, ou mais da maneira que este artigo irá tratar, via adb.
O que são bloatwares?
Bloatware é a junção das palavras bloat (inchar) + software (programa), ou seja, um bloatware é basicamente um programa inútil ou facilmente substituível — colocado em seu dispositivo previamente pela fabricante e operadora — que está no seu dispositivo apenas ocupando espaço de armazenamento, consumindo memória RAM e pior, coletando seus dados e enviando para servidores externos, além de serem mais pontos de vulnerabilidades.
O que é o adb?
O Android Debug Brigde, ou apenas adb, é uma ferramenta que se utiliza das permissões de usuário shell e permite o envio de comandos vindo de um computador para um dispositivo Android exigindo apenas que a depuração USB esteja ativa, mas também pode ser usada diretamente no celular a partir do Android 11, com o uso do Termux e a depuração sem fio (ou depuração wifi). A ferramenta funciona normalmente em dispositivos sem root, e também funciona caso o celular esteja em Recovery Mode.
Requisitos:
Para computadores:
• Depuração USB ativa no celular; • Computador com adb; • Cabo USB;
Para celulares:
• Depuração sem fio (ou depuração wifi) ativa no celular; • Termux; • Android 11 ou superior;
Para ambos:
• Firewall NetGuard instalado e configurado no celular; • Lista de bloatwares para seu dispositivo;
Ativação de depuração:
Para ativar a Depuração USB em seu dispositivo, pesquise como ativar as opções de desenvolvedor de seu dispositivo, e lá ative a depuração. No caso da depuração sem fio, sua ativação irá ser necessária apenas no momento que for conectar o dispositivo ao Termux.
Instalação e configuração do NetGuard
O NetGuard pode ser instalado através da própria Google Play Store, mas de preferência instale pela F-Droid ou Github para evitar telemetria.
F-Droid: https://f-droid.org/packages/eu.faircode.netguard/
Github: https://github.com/M66B/NetGuard/releases
Após instalado, configure da seguinte maneira:
Configurações → padrões (lista branca/negra) → ative as 3 primeiras opções (bloquear wifi, bloquear dados móveis e aplicar regras ‘quando tela estiver ligada’);
Configurações → opções avançadas → ative as duas primeiras (administrar aplicativos do sistema e registrar acesso a internet);
Com isso, todos os apps estarão sendo bloqueados de acessar a internet, seja por wifi ou dados móveis, e na página principal do app basta permitir o acesso a rede para os apps que você vai usar (se necessário). Permita que o app rode em segundo plano sem restrição da otimização de bateria, assim quando o celular ligar, ele já estará ativo.
Lista de bloatwares
Nem todos os bloatwares são genéricos, haverá bloatwares diferentes conforme a marca, modelo, versão do Android, e até mesmo região.
Para obter uma lista de bloatwares de seu dispositivo, caso seu aparelho já possua um tempo de existência, você encontrará listas prontas facilmente apenas pesquisando por elas. Supondo que temos um Samsung Galaxy Note 10 Plus em mãos, basta pesquisar em seu motor de busca por:
Samsung Galaxy Note 10 Plus bloatware listProvavelmente essas listas já terão inclusas todos os bloatwares das mais diversas regiões, lhe poupando o trabalho de buscar por alguma lista mais específica.
Caso seu aparelho seja muito recente, e/ou não encontre uma lista pronta de bloatwares, devo dizer que você acaba de pegar em merda, pois é chato para um caralho pesquisar por cada aplicação para saber sua função, se é essencial para o sistema ou se é facilmente substituível.
De antemão já aviso, que mais para frente, caso vossa gostosura remova um desses aplicativos que era essencial para o sistema sem saber, vai acabar resultando na perda de alguma função importante, ou pior, ao reiniciar o aparelho o sistema pode estar quebrado, lhe obrigando a seguir com uma formatação, e repetir todo o processo novamente.
Download do adb em computadores
Para usar a ferramenta do adb em computadores, basta baixar o pacote chamado SDK platform-tools, disponível através deste link: https://developer.android.com/tools/releases/platform-tools. Por ele, você consegue o download para Windows, Mac e Linux.
Uma vez baixado, basta extrair o arquivo zipado, contendo dentro dele uma pasta chamada platform-tools que basta ser aberta no terminal para se usar o adb.
Download do adb em celulares com Termux.
Para usar a ferramenta do adb diretamente no celular, antes temos que baixar o app Termux, que é um emulador de terminal linux, e já possui o adb em seu repositório. Você encontra o app na Google Play Store, mas novamente recomendo baixar pela F-Droid ou diretamente no Github do projeto.
F-Droid: https://f-droid.org/en/packages/com.termux/
Github: https://github.com/termux/termux-app/releases
Processo de debloat
Antes de iniciarmos, é importante deixar claro que não é para você sair removendo todos os bloatwares de cara sem mais nem menos, afinal alguns deles precisam antes ser substituídos, podem ser essenciais para você para alguma atividade ou função, ou até mesmo são insubstituíveis.
Alguns exemplos de bloatwares que a substituição é necessária antes da remoção, é o Launcher, afinal, é a interface gráfica do sistema, e o teclado, que sem ele só é possível digitar com teclado externo. O Launcher e teclado podem ser substituídos por quaisquer outros, minha recomendação pessoal é por aqueles que respeitam sua privacidade, como Pie Launcher e Simple Laucher, enquanto o teclado pelo OpenBoard e FlorisBoard, todos open-source e disponíveis da F-Droid.
Identifique entre a lista de bloatwares, quais você gosta, precisa ou prefere não substituir, de maneira alguma você é obrigado a remover todos os bloatwares possíveis, modifique seu sistema a seu bel-prazer. O NetGuard lista todos os apps do celular com o nome do pacote, com isso você pode filtrar bem qual deles não remover.
Um exemplo claro de bloatware insubstituível e, portanto, não pode ser removido, é o com.android.mtp, um protocolo onde sua função é auxiliar a comunicação do dispositivo com um computador via USB, mas por algum motivo, tem acesso a rede e se comunica frequentemente com servidores externos. Para esses casos, e melhor solução mesmo é bloquear o acesso a rede desses bloatwares com o NetGuard.
MTP tentando comunicação com servidores externos:
Executando o adb shell
No computador
Faça backup de todos os seus arquivos importantes para algum armazenamento externo, e formate seu celular com o hard reset. Após a formatação, e a ativação da depuração USB, conecte seu aparelho e o pc com o auxílio de um cabo USB. Muito provavelmente seu dispositivo irá apenas começar a carregar, por isso permita a transferência de dados, para que o computador consiga se comunicar normalmente com o celular.
Já no pc, abra a pasta platform-tools dentro do terminal, e execute o seguinte comando:
./adb start-serverO resultado deve ser:
daemon not running; starting now at tcp:5037 daemon started successfully
E caso não apareça nada, execute:
./adb kill-serverE inicie novamente.
Com o adb conectado ao celular, execute:
./adb shellPara poder executar comandos diretamente para o dispositivo. No meu caso, meu celular é um Redmi Note 8 Pro, codinome Begonia.
Logo o resultado deve ser:
begonia:/ $
Caso ocorra algum erro do tipo:
adb: device unauthorized. This adb server’s $ADB_VENDOR_KEYS is not set Try ‘adb kill-server’ if that seems wrong. Otherwise check for a confirmation dialog on your device.
Verifique no celular se apareceu alguma confirmação para autorizar a depuração USB, caso sim, autorize e tente novamente. Caso não apareça nada, execute o kill-server e repita o processo.
No celular
Após realizar o mesmo processo de backup e hard reset citado anteriormente, instale o Termux e, com ele iniciado, execute o comando:
pkg install android-toolsQuando surgir a mensagem “Do you want to continue? [Y/n]”, basta dar enter novamente que já aceita e finaliza a instalação
Agora, vá até as opções de desenvolvedor, e ative a depuração sem fio. Dentro das opções da depuração sem fio, terá uma opção de emparelhamento do dispositivo com um código, que irá informar para você um código em emparelhamento, com um endereço IP e porta, que será usado para a conexão com o Termux.
Para facilitar o processo, recomendo que abra tanto as configurações quanto o Termux ao mesmo tempo, e divida a tela com os dois app’s, como da maneira a seguir:
Para parear o Termux com o dispositivo, não é necessário digitar o ip informado, basta trocar por “localhost”, já a porta e o código de emparelhamento, deve ser digitado exatamente como informado. Execute:
adb pair localhost:porta CódigoDeEmparelhamentoDe acordo com a imagem mostrada anteriormente, o comando ficaria “adb pair localhost:41255 757495”.
Com o dispositivo emparelhado com o Termux, agora basta conectar para conseguir executar os comandos, para isso execute:
adb connect localhost:portaObs: a porta que você deve informar neste comando não é a mesma informada com o código de emparelhamento, e sim a informada na tela principal da depuração sem fio.
Pronto! Termux e adb conectado com sucesso ao dispositivo, agora basta executar normalmente o adb shell:
adb shellRemoção na prática Com o adb shell executado, você está pronto para remover os bloatwares. No meu caso, irei mostrar apenas a remoção de um app (Google Maps), já que o comando é o mesmo para qualquer outro, mudando apenas o nome do pacote.
Dentro do NetGuard, verificando as informações do Google Maps:
Podemos ver que mesmo fora de uso, e com a localização do dispositivo desativado, o app está tentando loucamente se comunicar com servidores externos, e informar sabe-se lá que peste. Mas sem novidades até aqui, o mais importante é que podemos ver que o nome do pacote do Google Maps é com.google.android.apps.maps, e para o remover do celular, basta executar:
pm uninstall –user 0 com.google.android.apps.mapsE pronto, bloatware removido! Agora basta repetir o processo para o resto dos bloatwares, trocando apenas o nome do pacote.
Para acelerar o processo, você pode já criar uma lista do bloco de notas com os comandos, e quando colar no terminal, irá executar um atrás do outro.
Exemplo de lista:
Caso a donzela tenha removido alguma coisa sem querer, também é possível recuperar o pacote com o comando:
cmd package install-existing nome.do.pacotePós-debloat
Após limpar o máximo possível o seu sistema, reinicie o aparelho, caso entre no como recovery e não seja possível dar reboot, significa que você removeu algum app “essencial” para o sistema, e terá que formatar o aparelho e repetir toda a remoção novamente, desta vez removendo poucos bloatwares de uma vez, e reiniciando o aparelho até descobrir qual deles não pode ser removido. Sim, dá trabalho… quem mandou querer privacidade?
Caso o aparelho reinicie normalmente após a remoção, parabéns, agora basta usar seu celular como bem entender! Mantenha o NetGuard sempre executando e os bloatwares que não foram possíveis remover não irão se comunicar com servidores externos, passe a usar apps open source da F-Droid e instale outros apps através da Aurora Store ao invés da Google Play Store.
Referências: Caso você seja um Australopithecus e tenha achado este guia difícil, eis uma videoaula (3:14:40) do Anderson do canal Ciberdef, realizando todo o processo: http://odysee.com/@zai:5/Como-remover-at%C3%A9-200-APLICATIVOS-que-colocam-a-sua-PRIVACIDADE-E-SEGURAN%C3%87A-em-risco.:4?lid=6d50f40314eee7e2f218536d9e5d300290931d23
Pdf’s do Anderson citados na videoaula: créditos ao anon6837264 http://eternalcbrzpicytj4zyguygpmkjlkddxob7tptlr25cdipe5svyqoqd.onion/file/3863a834d29285d397b73a4af6fb1bbe67c888d72d30/t-05e63192d02ffd.pdf
Processo de instalação do Termux e adb no celular: https://youtu.be/APolZrPHSms
-
 @ 04c915da:3dfbecc9
2025-05-20 15:50:22
@ 04c915da:3dfbecc9
2025-05-20 15:50:22There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 91117f2b:111207d6
2025-05-20 15:27:21
@ 91117f2b:111207d6
2025-05-20 15:27:21
Mata mask is a very popular digital wallet and power extension which allows users to interact with etherium the blockchain and other compatible networks. In this article we will explore the benefits and features of using Meta mask,as and also provide a step by step on how to get started.
WHAT IS META MASK MANY will ask what is meta mask, it is a soft ware wallet which allows the users to receive store and also send etherium and other tokens. You can find them in your browsers like playstore Google chrome and so on.
THEY ARE KEY FEATURES WHEN USING A META MASK 1. BLOCKCHAIN INTERACTIONS : meta mask allows you to interact with decentralized applications and also smart contracts on etherium blockchain. 2. CUSTOMIZABLE:meta mask allows the user to hod or her experience and choosing which networks to interact with. 3. SECURE STORAGE: metamask stores your privately key securely, allowing you to make use of your digital assets with confidence.
THE BENEFITS OF USING META MASK 1. NFTs: meta mask allows you to buy, sell and store no fungible tokens 'nft' on platforms like rarible and so on.
-
DECENTRALIZED FINANCE: meta mask allows you to access a large range of decentralized applications including trading, and borrowing and also trading platforms.
-
SMART CONTRACTS INTERACTIONS: meta mask also allows you to interact with decentralized governance and other blockchain-based applications.
WHEN GETTING STARTED WITH META MASK 1. Install the meta mask app 2. Create a wallet. 3. Fund your wallet by transferring etherium or other supported tokens to your wallet. 4. Explore the app by browsing decentralized applications and smart contracts on the etherium blockchain.
IN conclusion, meta mask is suitable for anyone looking to interact with etherium blockchain and other compatible networks. It is also suitable for anyone who is interested in decentralized finance, smart contracts interactions even NFTs.
-
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ cae03c48:2a7d6671
2025-05-20 15:26:52
@ cae03c48:2a7d6671
2025-05-20 15:26:52Bitcoin Magazine

Standard Chartered Backs $500K Bitcoin Target, Citing Growing Government Exposure Through MSTRSovereign investment in Bitcoin is accelerating—just not always in the most direct way. In a new report, Standard Chartered Bank says indirect exposure via Strategy (formerly MicroStrategy) is quietly increasing among government entities, reinforcing the bank’s long-standing price prediction that Bitcoin will reach $500,000 before President Donald Trump leaves office in 2029.
JUST IN:
 Standard Chartered says SEC 13F fillings support #Bitcoin reaching $500,000 by 2028
Standard Chartered says SEC 13F fillings support #Bitcoin reaching $500,000 by 2028  pic.twitter.com/MURg9bxLka
pic.twitter.com/MURg9bxLka— Bitcoin Magazine (@BitcoinMagazine) May 20, 2025
“The latest 13F data from the U.S. Securities and Exchange Commission (SEC) supports our core thesis that Bitcoin (BTC) will reach the $500,000 level before Trump leaves office as it attracts a wider range of institutional buyers,” wrote Geoffrey Kendrick, Standard Chartered’s global head of digital assets research. “As more investors gain access to the asset and as volatility falls, we believe portfolios will migrate towards their optimal level from an underweight starting position in BTC.”
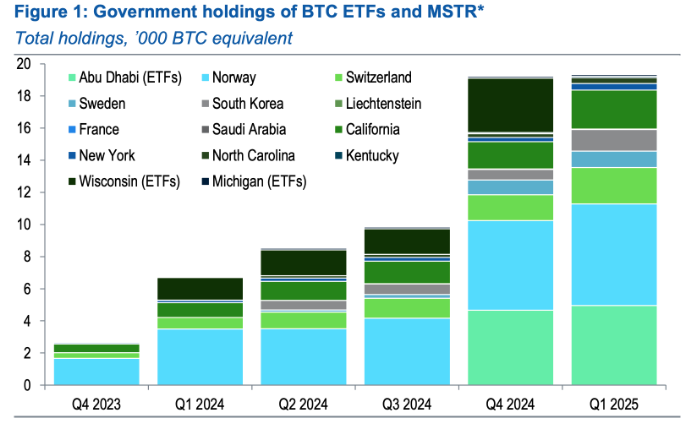
Q1 13F filings revealed a slowdown in direct bitcoin ETF buying—Wisconsin’s state fund exited its entire 3,400 BTC-equivalent IBIT position—while government-linked purchases of MSTR shares were on the rise. Abu Dhabi’s Mubadala, for instance, upped its IBIT exposure to 5,000 BTC equivalent, but Kendrick says the bigger story is elsewhere.
“We believe that in some cases, MSTR holdings by government entities reflect a desire to gain Bitcoin exposure where local regulations do not allow direct BTC holdings,” he said.
France and Saudi Arabia took first-time MSTR positions in Q1. Meanwhile, Norway’s Government Pension Fund, the Swiss National Bank, and South Korea’s public funds each added exposure equivalent to 700 BTC. U.S. retirement funds in states like California and New York added a combined 1,000 BTC equivalent via MSTR. Kendrick called the trend “very encouraging.”
“The quarterly 13F data is the best test of our thesis that BTC will attract new institutional buyer types as the market matures, helping the price reach our USD 500,000 level,” Kendrick said. “When institutions buy Bitcoin, prices tend to rise.”
SEC DATA BACKS BITCOIN $500K TARGET BY 2028: STANDARD CHARTERED
Standard Chartered's Geoff Kendrick says recent SEC 13F filings support a possible rise in Bitcoin to $500,000 by end-2028. While direct ETF holdings dipped in Q1, government entities boosted stakes in Strategy…
— *Walter Bloomberg (@DeItaone) May 20, 2025
This isn’t Kendrick’s first bullish call. Last month, he admitted his prior $120K forecast for Q2 2025 was “too low,” citing surging inflows into U.S. spot BTC ETFs—totaling $5.3 billion over just three weeks. At the time, Kendrick revised his 2025 year-end target to $200,000.
Standard Chartered’s latest analysis shows that Bitcoin’s role in institutional portfolios is maturing beyond tech volatility correlation—now increasingly seen as a macro hedge. “It is now all about flows,” Kendrick said. “And flows are coming in many forms.”
This post Standard Chartered Backs $500K Bitcoin Target, Citing Growing Government Exposure Through MSTR first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ 2e8970de:63345c7a
2025-05-20 15:19:25
@ 2e8970de:63345c7a
2025-05-20 15:19:25https://www.wsj.com/tech/europe-big-tech-ai-1f3f862c?mod=hp_lead_pos7
https://stacker.news/items/984656
-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ 4fa5d1c4:fd6c6e41
2025-05-20 15:13:35
@ 4fa5d1c4:fd6c6e41
2025-05-20 15:13:35📌 Ablauf
1. Prompt auswählen
Wähle aus der Promptsammlung einen Prompt, der dich anspricht – z. B. zu Unterrichtsplanung, Kreativmethoden, Inklusion oder KI-Nutzung im RU.
2. Prompt ausprobieren
Verwende den Prompt mit einem KI-Tool (z. B. ChatGPT oder ein freies Modell wie LM Studio) und passe ihn ggf. leicht an dein Thema oder deine Klasse an.
3. Reflexion schreiben
Notiere kurz, was gut geklappt hat, was überrascht hat oder was du noch verbessern möchtest. Halte es so fest, dass andere davon lernen können.
4. Auf Nostr posten
Veröffentliche deine Reflexion oder ein konkretes Ergebnis (z. B. Screenshot, kurzer Textauszug, Sketchnote …) über deinen Nostr-Client (z. B. Damus, Amethyst, Habla.news).\ Verwende folgende Hashtags:
```text
relilab #verstehen oder #anwenden oder #reflektieren oder #gestalten
(optional: 1️⃣, 2️⃣ oder 3️⃣ je nach Niveaustufe) ```
Beispiel:
markdown Heute mit dem Prompt zur „Virtuellen Exkursion“ gearbeitet – mega spannend, wie viel die Schüler:innen zu Jerusalem wussten! Habe das Ergebnis als Audio-Reisebericht umgesetzt. #relilab #anwenden 2️⃣
💡 Hinweise
-
Nutze möglichst einen Prompt pro Post, damit die Community gut filtern kann.
-
Wenn du einen neuen Prompt ausprobierst oder abwandelst, verlinke gerne auf die Originalquelle (z. B. „Kapitel 2 · Kreative Unterrichtsgestaltung – Lernspiel entwickeln“).
-
Du kannst auch Fragen an die Community stellen: z. B. „Hat jemand diesen Prompt schon mal mit einer 6. Klasse ausprobiert?“
📣 Ziel der Aktion
Durch eure Beiträge entsteht eine wachsende Sammlung an:
-
reflektierten Einsatzbeispielen aus der Praxis
-
kreativen Varianten und Weiterentwicklungen
-
Ideen für KI-gestützte Lehrer:innenbildung im Fach Religion
Wenn du magst, notiere deine eigenen Favoriten-Prompts, poste Screenshots oder gestalte eine „Best-of“-Sammlung für dein Kollegium!
Promptsammlung Religionsunterricht
Kapitel 1 · Unterrichtsplanung & -vorbereitung (Religionsunterricht)
Religionsstunde planen
prompt Plane eine 45-minütige Religionsstunde in **[Klassenstufe]** zum Thema **[„Nächstenliebe in Judentum, Christentum & Islam“ o. ä.]**. Liefere: – drei messbare Kompetenzziele (KMK-Bereich „Religiöse Identität entwickeln“) – detaillierten Phasenplan (Einstieg | Erarbeitung | Sicherung | Transfer) mit Zeitangaben – mindestens zwei kreative Sozialformen (Think-Pair-Share, Placemat, Gallery Walk …) – Kerntext(e) aus Bibel, Koran oder Tanach + passenden Medienimpuls (Video, Bild, Song) – Lernaufgabe für zu Hause, die das Thema in den Lebenswelt-Bezug bringtUnterrichtseinheit entwerfen
prompt Entwirf eine vierwöchige Einheit **[Thema: „Schöpfungsverantwortung“]** für die **[Sek I]**. Für jede Doppelstunde angeben: – Leitfrage & erwartetes Kompetenzniveau (AB I – III) – Schlüsseltexte/Traditionen (Genesis 1–2, islamische Schöpfungs-Ayat, „Laudato si’“ …) – handlungsorientierte Lernaufgabe inkl. Differenzierung – Methodensetting (z. B. Gruppenpuzzle, Mystery, Stationenlauf) – benötigte Materialien/Medien und eine kurze ReflexionsideeDifferenzierte Lernaufgaben
prompt Formuliere Lernaufgaben zum Thema **[„Gleichnisse Jesu“]** für drei Anspruchsniveaus: 1. Unterstützungsniveau – Lesestrategieblatt + vorstrukturierter Lückentext 2. Basisniveau – Text-Puzzle + Placemat-Diskussion 3. Erweiterungsniveau – eigener Podcast (Recherche, Skript, Produktion, Peer-Feedback) Je Aufgabe: Ziel, Ablauf in Schritten, erwartetes Produkt, Bewertungsfokus.Langfristiges Projekt skizzieren
prompt Skizziere ein sechs-wöchiges Projekt **„Interreligiöse Stadt-Rallye“** für **[Klasse 9]**: – Projektziele & zugeordnete Kompetenzen – Checkliste für Besuche (Kirche, Synagoge, Moschee, Tempel) inkl. Leitfragen – digitale Dokumentation (Padlet-Storyboard, QR-Blogposts, Foto-Missionen) – Abschlussprodukt (multimediale Stadttour) + Rubrik mit vier BewertungsdimensionenJahresübersicht erstellen
prompt Erstelle eine Grobjahresplanung für **[ev. Religion, Kl. 5]** mit sechs Themenfeldern (z. B. „Staunen über die Schöpfung“, „Jesus begegnen“…). Zu jedem Feld: – Zeitraum & passendes Fest im Kirchenjahr als Anker – kompetenzorientierte Leistungsform (Portfolio, Lernlandkarte, Präsentation …) – kurze Hinweissequenz für mögliche fächerverbindende ChancenProjektwoche „Spiritualität erleben“
prompt Konzipiere eine fächerübergreifende Projektwoche **„Spiritualität & Achtsamkeit“** für **[Jgst. 7–8]**: – Workshop-Menü (Ikonenmalen, Kalligraphie, Yoga, Psalm-Rap, MBSR-Übungen …) – externe Expert*innen (Pfarrer*in, Imam, Rabbiner*in, buddhistische*r Lehrer*in) – tägliche Reflexionsformate (Stille-Tagebuch, Audio-Log, Blitzlicht-Runde) – gemeinsamer Abschluss: interreligiöses Friedensgebet + Feedback-GalleryKompetenzen formulieren
prompt Schreibe messbare Kompetenzformulierungen für die Einheit **[„Propheten – Stimmen für Gerechtigkeit“]** (Sek II). Nutze Anforderungsbereiche I–III und füge zu jeder Kompetenz: Beobachtungshinweis + kurzes Beispiel für Leistungsnachweis.
Kapitel 2 · Kreative Unterrichtsgestaltung (Religionsunterricht)
Lernspiel entwickeln
prompt Entwickle ein interaktives Spiel, das Schüler*innen **[z. B. die Zehn Gebote]** niedrigschwellig erarbeiten lässt. Beschreibe: Spielidee, Regeln, Material, Spielphasen (Warm-up | Action | Debrief) und Reflexionsfragen zur theologischen Vertiefung.Gruppenarbeit strukturieren
prompt Plane eine Gruppenaufgabe zu den **„Seligpreisungen der Bergpredigt“**: – Gruppenzuteilung je Seligpreisung – Produktwahl (Comic-Strip, Poetry-Slam, Kurzvideo …) mit Kreativbriefing – Präsentations-Setting + Peer-Feedback-Raster – Lehrer*innen-Checkliste zur Beobachtung von Zusammenarbeit & InhaltstiefeInterdisziplinärer Unterricht
prompt Kombiniere **„Umweltschutz in den Weltreligionen“** mit **Biologie** in einer Doppelstunde: – theologischer Impuls (Schöpfungsverantwortung) – biologischer Faktenblock (ökologische Fußabdrücke) – Arbeitsphase: Lernende vergleichen religiöse & wissenschaftliche Begründungen und entwerfen Handlungsideen für die Schule.Storytelling einsetzen
prompt Zeige, wie Storytelling das Thema **„Exodus – Befreiungsgeschichte“** lebendig macht: – Dramaturgie (Setup – Konflikt – Climax – Rückbindung) – Erzähler*innenrollen (Miriam, Moses, Pharao, Gott als Off-Stimme) – Aufgaben: Storyboard zeichnen, Rollen-Podcast aufnehmen, reflektiertes JournalExperimenteller Ansatz
prompt Entwirf einen experimentellen Unterrichtsgang zur Leitfrage **„Was bedeutet heilig?“**: – Alltagsobjekte auswählen und symbolisch umdeuten lassen – Stationen: Wahrnehmung | Gestaltung | Deutung | Religionsvergleich – abschließende Reflexion in einem Gallery Walk + theologischer EinordnungBlended-Learning-Konzept
prompt Erstelle ein Blended-Learning-Szenario zur Einheit **„Feste im Kirchenjahr“**: – Online-Phase: interaktive Zeitleiste, Erklärvideos, H5P-Quiz – Präsenz-Phase: Lernlandkarte, Gruppen-Challenge „Festkalender bauen“ – Leistungsnachweis: Lerntagebuch + digitale Portfolio-AbgabeDesign Thinking anwenden
prompt Nutze Design Thinking, um mit Schüler*innen Lösungen für **„Armut in unserer Stadt“** aus religiöser Perspektive zu entwickeln. Beschreibe alle sechs Phasen inkl. Tools (Empathy Map, How-Might-We-Fragen, Prototyping-Material), Zeit- und Raumplan.Escape-Room planen
prompt Konzipiere einen pädagogischen Escape Room zum Thema **„Paulus auf Missionsreise“**: – Storyline (Start, Hinweise, Wendepunkt, Finale) – fünf Rätseltypen (Logik, Bibelcode, UV-Botschaft …) – benötigtes Material & Technik + Safety-Briefing – Auswertungsbogen für Lernergebnisse & Teamwork-SkillsFlipped Classroom umsetzen
prompt Gestalte einen Flipped-Classroom-Ablauf zur Einheit **„Gleichnisse Jesu“**: – Zuhause: drei Micro-Learning-Videos (< 5 min) + interaktiver Selbsttest – Unterricht: kooperative Fallanalyse, Rollenspiel, Kreativstation – Reflexion: One-Minute-Paper → digitales Feedback-PadVirtuelle Exkursion einbauen
prompt Baue eine virtuelle Exkursion **„Jerusalem – Heilige Stätten“** ein: – Ressourcen: 360°-VR-Tour, Street-View-Links, Museums-App – Vorbereitende Leitfragen (historisch, religiös, politisch) – Arbeitsauftrag: digitale Reise-Map anlegen, Eindrücke vertonen, Peer-Review – Abschluss: Fishbowl-Diskussion zu religiöser Vielfalt & KonfliktlinienKapitel 3 · Differenzierung & Inklusion (Religiöses Lernen)
Inklusive Aufgabenstellung
prompt Gestalte eine Unterrichtseinheit zu **[„Gleichnisse Jesu“]** so, dass Lernende mit kognitiven, motorischen oder sprachlichen Beeinträchtigungen aktiv teilnehmen können. • beschreibe drei barrierearme Medien-/Methoden-Anpassungen • formuliere für jedes Lernniveau ein messbares Teilziel • gib Beispiele für unterstützende Hilfsmittel (z. B. Symbolkarten, Audiodeskription, taktile Bibel)Individuellen Förderplan erstellen
prompt Erstelle einen Förderplan für eine*n Schüler*in mit Lese-Rechtschreib-Schwäche im Thema **[„Schöpfungspsalmen“]**: – diagnostische Ausgangslage + SMART-Ziele – wöchentliche Lernschritte (Methoden, Materialien, Zeitbudget) – Evaluationskriterien & Reflexionsfragen für Lernende + LehrkraftKompetenzentwicklung begleiten
prompt Zeige, wie du die Kompetenzentwicklung in der Einheit **„Spiritualität & Achtsamkeit“** laufend beobachtest: • Portfolio-Raster mit Indikatoren zu Wahrnehmung / Deutung / Gestaltung • Feedback-Tool (Ampel, Check-Out, Audio-Memo) • Maßnahmenplan bei Unter- oder ÜberforderungPersonalisierte Lernpfade
prompt Baue personalisierte Lernpfade für **„Weltreligionen im Dialog“** (Kl. 7) auf: – drei optionale Module (Video-Recherche, Expert*innen-Interview, Kreativprodukt) je nach Vorwissen – Self-Assessment-Checkpoints + Empfehlung nächster Schritt – technische Umsetzung mit Learning-Management-System deiner WahlLernjournal nutzen
prompt Entwirf ein Lernjournal-Format zur Reihe **„Seligpreisungen“**: • tägliche Prompt-Frage (kognitiv, affektiv, spirituell) • visuelle Elemente (Sketchnote, Emojikarte, Farbsymbol) • Wochen-Meta-Reflexion + Peer-KommentarfeldSpezifische Unterstützung
prompt Beschreibe Zusatzmaßnahmen, um das abstrakte Konzept **„Trinität“** für Lernende mit Verständnisschwierigkeiten greifbar zu machen: – vereinfachte Grafiken, Alltagsanalogien, szenische Darstellung – Schritt-für-Schritt-Erklärvideo (max. 3 min) – begleitender Glossar in einfacher SpracheKulturelle Vielfalt einbeziehen
prompt Plane eine Sequenz **„Feste im Jahreskreis“** so, dass christliche, jüdische und muslimische Perspektiven gleichwertig vorkommen. Gib drei konkrete Aufgabenbeispiele (interaktiver Wandkalender, Interview mit Familie, „Fest-Box“) und nenne Bewertungsbausteine zur Würdigung kultureller Vielfalt.Mehrsprachigkeit fördern
prompt Zeige Strategien, wie du arabisch-, hebräisch- oder russischsprachige Schüler*innen in das Thema **„Friede in den Heiligen Schriften“** einbeziehst: – zweisprachiger Wortschatz-Trainer – Tandem-Aktivität mit Übersetzer-App – Produktoption „mehrsprachiges Audio-Gebet“Barrierefreier Unterricht
prompt Erstelle einen barrierefreien Ablaufplan für eine 90-min-Sequenz zu **„Luther und die Reformation“** in einer heterogenen Lerngruppe: – Raum-, Material- und Technik-Anpassungen – klare Kommunikationsregeln (z. B. Gebärdensprach-Dolmetsch, Live-Untertitel) – evaluierbare Barrierefreiheits-ChecklisteKapitel 4 · Bewertung & Feedback (im Religionsunterricht)
Prüfungsfragen entwickeln
prompt Formuliere fünf Prüfungsaufgaben zu **„Prophetische Bücher“** (2 Wissen, 2 Transfer, 1 Bewertung). Gib zu jeder Aufgabe Erwartungshorizont & Bloom-Taxonomie-Stufe an.Lernstrategien für Schüler*innen
prompt Erstelle drei konkrete Tipps, wie sich Lernende auf eine Klassenarbeit zu **„Kirchengeschichte – Reformation bis heute“** vorbereiten können (visualisieren | vernetzen | reflektieren).Selbstbewertung anleiten
prompt Entwirf einen Selbstbewertungsbogen, mit dem Oberstufen-Schüler*innen ihre persönliche spirituelle Entwicklung in der Einheit **„Exodus – Freiheit erleben“** reflektieren: – 5 Skalen-Items + offenes Feld – Anleitungs-Text für ehrliche Selbsteinschätzung – Follow-Up-GesprächsleitfadenPeer-Feedback organisieren
prompt Baue ein Peer-Feedback-Setting für das Projekt „Predigt-Podcast zur Nächstenliebe“ auf: • 3-Kriterien-Checkliste (Inhalt, theologischer Tiefgang, Medieneinsatz) • Zeit-Taktung (Aufnahme – Austausch – Revision) • Moderationskarten für konstruktive RückmeldungBewertungsrubrik erstellen
prompt Entwerfe eine 4-stufige Rubrik für das Produkt **„Interreligiöser Video-Essay: Was ist heilig?“** Bewertungsdimensionen: Recherche, Argumentation, Kreativität, Technik. Ordne jeder Stufe klare Deskriptoren & Punktwerte zu.Schnelle Lernüberprüfung
prompt Skizziere eine 3-Min-Exit-Ticket-Abfrage zum Stundenthema **„Auferstehungshoffnung“**: – eine Verständnisfrage, ein Transfer-Impuls, ein persönlicher Bezug – Auswertungsplan (Ampel-Sortierung + Blitz-Feedback an Klasse)Feedback von Schüler*innen einholen
prompt Erstelle fünf Leitfragen, um anonymes Lernenden-Feedback zum Thema **„Sakrale Räume erkunden“** zu sammeln (Aspekte: Klarheit, Relevanz, Methoden, Beteiligung, Wohlbefinden). Schlage ein digitales Tool für die Umsetzung vor und erläutere den Ablauf in 3 Schritten.Kapitel 5 · Digitale Medien & KI (Religionsunterricht)
Interaktive Biblemap erstellen
prompt Lege mit **[Tool: Thinglink / Genially]** eine interaktive Karte biblischer Orte an (Jerusalem, Nazareth, Bethsaida …). – je Ort: Kurzinfo, Bild/360°-Link, passender Bibelvers – Aufgabe: Lernende verknüpfen Geodaten mit Lebensstationen Jesu – füge Reflexionsfragen + Export-Anleitung für das LMS hinzuKI-ChatBot als Lernpartner
prompt Konfiguriere einen KI-ChatBot, der Fragen zu **„Weltreligionen und Umweltschutz“** auf A2–B2-Sprachniveau beantwortet. – Prompt-Engineering-Vorgabe (Rolle, Stil, Quellenzitierweise) – fünf Beispiel-User-Prompts + erwartete Bot-Antwort – Datenschutz-Hinweis & didaktischer EinsatzrahmenBibel-Snap-AR-Filter entwickeln
prompt Entwirf ein Konzept für einen Augmented-Reality-Filter (Instagram/Snap) zu **„Seligpreisungen“**: – visuelle Overlays, Trigger-Events, Soundeffekt – Lernaufgabe: Selfie mit Lieblingsseligpreisung + Kommentar posten – Ethik-Checkliste (Privatsphäre, Bildrechte, Sensibilität religiöser Symbole)Digitales Escape-Game bauen
prompt Plane mit **[Tool: Deck.Toys]** ein digitales Escape-Game „Spuren des Propheten Jesaja“: – Level-Struktur (Prophetie-Puzzle, Quiz, Hidden Object) – win-Condition & automatisiertes Feedback – Export-Code + Anleitung für barrierefreie Version (Screenreader-Labels)Podcast-Serie kuratieren
prompt Stelle eine 4-teilige Schüler-Podcast-Serie **„Gerechtigkeit in Religionen“** auf: – redaktioneller Plan (Themen, Gäste, Bibel/Koran-Bezüge) – Work-Flow (Skript, Aufnahme, Schnitt, Distribution) – Bewertungsrubrik – Inhalt, Technik, DiskursqualitätVirtuelles Museumslabor
prompt Nutze **Mozilla Hubs** und erstelle einen VR-Raum „Symbole des Glaubens“. – Raum-Zonen (Kreuz, Menora, Halbmond, Om) – Lehrer-Dashboard: Moderations-Tools + Sicherheits-Settings – Arbeitsauftrag: Lernende hinterlegen Audiokommentar & Quizfrage pro SymbolKI-gestützte Bildanalyse
prompt Zeige, wie Lernende mit **Computer-Vision-API** ikonografische Motive (z. B. Verkündigungsbild) analysieren: – Schrittanleitung: Upload → Tagging → theologische Interpretation – Vergleich mit manueller Bildbetrachtung – Reflexionsbogen zu Chancen & Grenzen automatischer Deutung
Kapitel 6 · Motivation & Klassenklima (im Religionsunterricht)
Einstieg mit Mystery-Bild
prompt Starte die Einheit **„Exodus“** mit einem rätselhaften Bildausschnitt (gezoomte Wüste, brennender Dornbusch …). – drei Leitfragen zum Rätsel – Ablauf Mystery-Methode (Hypothesen, Puzzleteile, Auflösung) – Brücke zur LernzieltransparenzRitual „Wort des Tages“
prompt Führe ein tägliches Ritual ein: Zufalls-Bibelvers via App, kurze stille Lesephase, spontanes Wort-Cloud-Feedback. – Setup-Anleitung, Regelzeit (3 min), Variationen (Hadith/Zitat) – Reflexion nach vier Wochen (Exit-Ticket-Vorlage)Gamifizierte Punkte-Challenge
prompt Erstelle ein Punktesystem („Faith-Coins“) für vorbildliches Teamwork in Projekten **„Interreligiöser Dialog“**: – Mission-Board, Badges, Level-Belohnungen – klare Regeln (Fairplay, Bonus für Hilfsbereitschaft) – Monitoring-Tool & Schutz vor Wettbewerb-StressAffirmations-Station
prompt Richte im Klassenraum eine „Mut-&-Segen-Station“ ein: – Materialliste (Segen-Karten, Affirmations-Würfel, Kerze) – Nutzung: Start/Ende der Stunde, bei Konflikten – Dokumentiere Wirkung mit anonymem Feedback-PosterKlassensong komponieren
prompt Lass die Klasse einen Song zu **„Nächstenliebe“** schreiben / recorden: – Schrittfolge: Brainstorm–Lyrics–Beat-Making–Recording–Release – Tools (Soundtrap, BandLab, Loop-Bibliothek CC-Lizenz) – Präsentation im Schul-Gottesdienst + Rechte-CheckDankbarkeits-Journal
prompt Implementiere ein wöchentliches Dankbarkeits-Journal nach der Stunde **„Schöpfung bewahren“**: – drei Leitfragen (Wahrnehmung, Wertschätzung, Umsetzung) – Peer-Sharing-Option (freiwillig) – Beobachtung: Einfluss auf Klassenklima (Mess-Skala beilegen)Konfliktlösungs-Circle
prompt Nutze eine Circle-Time nach der Methode „Restorative Justice“ bei Streit um religiöse Themen: – Rollen (Keeper, Sprecher*in, Zuhörer*in) – Gesprächsregeln & Talking-Piece – Nachbereitung: individueller Commitment-Zettel
Kapitel 7 · Spiritualität & Persönlichkeitsbildung
Meditation anleiten
prompt Schreibe ein 10-min-Skript für eine geführte Meditation „Ruhe finden – Psalm 23“, altersgerecht **[Klasse 8]**: – Setting (Sitzhaltung, Musik, Licht) – verbale Anleitung (Ein-, Ausatmen, Bild-Metaphern) – Nachbesprechung (Gefühls-Skala, Bibel-Resonanzfrage)Pilgerweg auf dem Schulhof
prompt Plane einen Mini-Pilgerweg (6 Stationen) zu „Fragen nach dem Sinn“ auf dem Gelände: – Stationstexte + Symbol-Aktion (Stein legen, Wasser berühren …) – QR-Codes mit Audioguide durch Schüler*innen eingesprochen – Reflexionsbogen + Foto-Collage-AufgabeStilles Tagebuch digital
prompt Setze mit **Padlet** ein „Stilles Tagebuch“ auf: – geschlossene Kommentarfunktion – wöchentliches Impulsbild (Ikone, Naturfoto, Calligraffiti) – Lehrkraft-Feedback nur per Emoji-Code, um Raum zu lassenGebetsformen erkunden
prompt Entwickle eine Lernstationen-Werkstatt **„Gebet in 5 Religionen“**: – Materialien: Gebetsriemen, Gebetsteppich, Mala-Kette, Kerzen, Textblätter – QR-Video-Tutorials zu Körperhaltungen – Reflexionsauftrag: Venn-Diagramm Gemeinsamkeiten/VerschiedenheitenSpirituelles Tage-Retreat
prompt Skizziere einen schulischen Tages-Retreat „Stille & Kreativität“ für Oberstufe: – Rhythmus: Meditation – Kreativ-Workshop – Solo-Waldzeit – Sharing-Circle – Logistik (Räume, Materialien, externe Begleitung) – Evaluations-Tool: digitales Mood-BarometerDank-Labyrinth bauen
prompt Gib Anweisungen, wie eine Klasse ein begehbares Dankbarkeits-Labyrinth aus Kerzen/Seilen legt: – Aufbauplan & Sicherheitsregeln – Impulstext „Preis der Dankbarkeit“ (Lk 17, 11-19) – Audio-Begleitung + ZeitplanLebensweg-Timeline gestalten
prompt Lass Lernende eine „Lebensweg-Timeline“ (Canvas / Miro) erstellen, in der spirituelle Schlüsselmomente eingetragen werden: – Anleitung zu Life-Events, Werte, Glaubensfragen – Peer-Coaching-Leitfaden (respektvolle Rückfragen) – Datenschutz-Vereinbarung & Freigabe-OptionenKapitel 8 · Soziale & emotionale Unterstützung (Religionsunterricht)
Emotionale Intelligenz fördern
prompt Entwirf eine 20-min-Aktivität, die Lernende der **[Klassenstufe]** dabei unterstützt, Gefühle mit Psalm-Metaphern auszudrücken. – Warm-up: Emoji-Kärtchen + passender Psalmvers – Partneraustausch „Wann habe ich mich wie König David gefühlt?“ – Mini-Reflexion: Gebets-Haiku (3 Zeilen) ins Klassen-Padlet postenKonfliktlösung interreligiös
prompt Stelle einen 3-Schritt-Leitfaden für Klassengespräche bei Spannungen zwischen religiösen Gruppen zusammen: 1. „Wertschätzungs-Runde“ – jede*r nennt, was er/sie an der anderen Tradition bewundert 2. „Gemeinsamer Kern“ – Bibel-, Koran- oder Tora-Vers zum Thema Frieden lesen, Gemeinsamkeiten markieren 3. „Handlungsplan“ – Klasse legt zwei konkrete Fairness-Regeln festAchtsamkeit mit Psalm 46
prompt Schreibe ein 5-min-Achtsamkeitsskript „Sei still und erkenne Gott“ für den Stundenbeginn: Atem-Anker, Psalmwort wiederholen, 30 Sek. Stille, Abschluss-Frage in Still-Journal notieren.Teambuilding „Vertrau mir“
prompt Plane ein Teambuilding-Spiel, bei dem Partner*innen mit verbundenen Augen durch einen „Weg des Lichts“ aus Kerzen geführt werden. – Sicherheits-Checkliste – Spiritueller Debrief: Johannes 8,12 verknüpfenKrisenintervention – spiritueller Beistand
prompt Erstelle ein 4-Punkte-Handout für Lehrkräfte, wie sie bei plötzlicher Trauer in der Klasse handeln: • Präsenz zeigen – kurze Stille + Kerze entzünden • Offenes Ohr – kein theologisieren, nur zuhören • Ressourcen nennen – Schulseelsorge, Jugendpfarrer*in • Nachsorge – Memory-Box gestaltenSelbstwert stärken (Imago Dei)
prompt Formuliere eine Kreativaufgabe „Ich bin Bild Gottes“: Lernende gestalten ein Self-Portrait-Collage mit Bibel-Affirmationen, kurze Audio-Beschreibung aufnehmen, Gallery-Walk durchführen.Resilienz durch Glaubensgeschichten
prompt Gib einen Arbeitsauftrag, bei dem Schüler*innen eine biblische Figur wählen, deren Lebenskrise sie analysieren (Hiob, Ruth, Josef) und die Strategien auf heutige Situationen übertragen.
Kapitel 9 · Elternarbeit & Zusammenarbeit
Elternbrief „Religiöse Lernwege“
prompt Verfasse einen Elternbrief (max. 300 Wörter), der – das Halbjahresthema **[z. B. Gerechtigkeit in den Propheten]** erklärt – 2 Mitmach-Tipps für zuhause enthält (Familiengebet, Podcast) – QR-Link zur Materialsammlung bietetElternabend – interreligiöse Einheit vorstellen
prompt Erstelle eine Agenda (60 min) für einen Elternabend: • Begrüßung & Gebet der Religionen (5 min) • Lernziele & Methoden-Tour (15 min) • Mini-Workshop „Feste teilen“ (20 min) • Fragen & Feedback-Karten (15 min) • Segen zum Abschluss (5 min)Elternfeedback digital einholen
prompt Gestalte einen 7-Fragen-Forms-Fragebogen: Skalen (1–5) zu: Relevanz, Transparenz, Wertevermittlung, Medienmix + zwei offene Felder „Was lief gut?“ / „Wunsch für nächste Reihe“.Schwieriges Elterngespräch führen
prompt Entwirf einen Gesprächsleitfaden (Sandwich-Methode) für eine Diskussion über fehlende Hausaufgaben im Kontext Glaubensfest-Vorbereitungen.Elternmitarbeit im Projekt „Feste zu Hause“
prompt Skizziere ein Mitmach-Format, bei dem Familien ihre Festtraditionen per Video (max. 2 min) vorstellen; Sammel-Padlet, Klassen-Kompliment-Wand und Auszeichnung „Fest-Botschafter*in“.Familienkommunikation stärken
prompt Gib drei Übungen, wie Eltern religiöse Dialoge anstoßen können: • „Frage des Tages“-Glas • Gemeinsames Dankbarkeitsbuch • Podcast „3 Minuten Bibelimpuls“ beim Abendessen hörenEltern-Kind-Projekt „Heilige Orte“
prompt Plane ein Wochenend-Projekt: Familie besucht lokalen Sakralbau, füllt Reflexions-Worksheet aus, erstellt Foto-Story in CANVA; Präsentation im Unterricht, Peer-Feedback-Kriterien beilegen.
Kapitel 10 · Zeitmanagement & Organisation (Religionsunterricht)
Liturgische To-do-Liste
prompt Erstelle für die nächsten 4 Schulwochen eine Checkliste, die Unterricht, Gottesdienst-Vorbereitung und Schulfest (St. Martin) synchronisiert; inkl. Deadlines & Verantwortliche.45-min-Stundenplan fein takten
prompt Gliedere eine Stunde **[Thema Gleichnisse]** in 5-Min-Blöcke: Warm-up-Rätsel, Kurzimpuls, Gruppenpuzzle, Austausch, Transfer, Mini-Exit-Ticket – plus 2 min Puffer.Unterrichtsstruktur „Flow“
prompt Baue einen wiederkehrenden Ablauf mit kleinen Ritualen: • Ankommens-Kerze (1 min) • Learning Target (Tafel-Icon) • Aktiv-Phase • Stille-Minute • Segen-to-goÜbergänge mit Symbol
prompt Gib 3 Methoden, um Phasenwechsel per Klangschale, Lichtritual oder Vers-Einblendung zu signalisieren – inkl. Schüler-Assistenzplan.Prioritäten im Kirchenjahr setzen
prompt Lege fest, welche Themen vor Weihnachten abgeschlossen sein müssen und welche (Fastenzeit) ins zweite Halbjahr fallen – Schlagwort-Roadmap.Arbeitszeitplan für Lehrkraft
prompt Erstelle einen Wochenplan (Mo–So) mit festen Blöcken: Vorbereitung, Korrektur, Seelsorge-Termin, Me-Time; Ampel-Farbcode für Belastung; Reminder „Sabbat-Abend offline“.
Kapitel 11 · Persönliche Weiterbildung & Reflexion
Selbstreflexion als Religionslehrkraft
prompt Liste 5 Leitfragen (Theologie, Didaktik, Spiritualität, Beziehung, Innovation), die du jedes Quartal schriftlich beantwortest.Fortbildung „KI im Religionsunterricht“
prompt Stelle einen 3-Stufen-Lernpfad zusammen: 1) Online-MOOC (4 h) 2) Praxis-Webinar „Prompt-Design“ (2 h) 3) Kollegiale Umsetzungsschau (90 min) mit Reflexionsbogen. 4) MarkDown für Liascript-LernmodulBurnout-Prophylaxe spirituell
prompt Entwirf eine 7-Tage-Challenge: tägliche 10-min-Stille, Journaling „Segen des Tages“, Digital-Sonnenuntergang (kein Screen nach 21 Uhr) und wöchentlicher Spazier-Psalm.Teamteaching ökumenisch
prompt Gib eine Checkliste für Planung mit einer katholischen Kollegin: gemeinsame Lernziele, liturgische Sprache abstimmen, Rollenverteilung, Reflexions-Debrief.Microteaching „Kurzpredigt“
prompt Lege ein Format fest: 5-min-Mini-Homilie vor Kolleg*innen, Video-Feedback, zweifache Wiederholung nach Feed-Forward-Regeln.Jahresziele setzen
prompt Nutze SMART+LOVE-Schema (L-inked to faith, O-wned, V-alue-added, E-cological) für drei persönliche Entwicklungsziele und definiere Quartals-Checkpoints.Innovation: VR-Pilgerfahrt
prompt Skizziere, wie du in 60 min eine VR-Station an einem Pilgerort testest, Evaluation × 3 (Lerngewinn, Technik, Emotion), Nachbesprechung im Kollegium.Kapitel 12 · Exkursionen & Außerschulisches Lernen
Kloster-Tag organisieren
prompt Plane einen ganztägigen Klassenausflug in ein Benediktiner- oder Zisterzienser-Kloster. – Zeitplan (Laudes-Besuch, Führung, Arbeitsstation, Stundengebet, Gesprächsrunde) – Lernziele (Spiritualität erleben, klösterliche Werte reflektieren, Stille-Erfahrung) – Arbeitsaufträge: Audio-Interview mit Mönch/Nonne, Foto-Essay „Ora et Labora“ – Vor-/Nachbereitung im Unterricht (Vorwissen-Quiz, Reflexionsportfolio)Interreligiöse Stadt-Tour
prompt Entwirf eine dreistündige „House-of-Worship-Tour“ (Moschee – Synagoge – Kirche) für die [Jgst. 9–10]. – Routenplan, Zeiten, Ansprechpartner*innen, Kleidungshinweise – Leitfragen je Stopp (Architektur, Riten, Engagement in der Stadtgesellschaft) – digitale Begleitmap in Google My Maps / Actionbound – Reflexionsprodukt: gemeinsames „Code of Respect“-PosterMuseum der Religionen virtuell
prompt Nutze 3D-Rundgänge von **[Museum X]** und erstelle ein Lern-Webquest „Religiöse Symbole im Wandel“. – fünf Recherche‐Aufgaben mit Zeitlimit – Peer-Review: Padlet-Poster „Top 3 Überraschungen“ – Lehrer-Dashboard: Bewertungskriterien + ZugangslinksPilgerwanderung light
prompt Skizziere eine 8-km-Pilgerstrecke nahe der Schule. – sechs Stationen (Psalm-Rezitation, Naturmeditation, Segenswort …) – Materialliste (Pilgerpass, Stempel, Erste-Hilfe-Set) – Safety-Plan + Elterninfo – Abschluss: Lagerfeuer-Runde „Reiseroute des Herzens“Service-Learning bei der Tafel
prompt Verbinde eine Exkursion zur lokalen Tafel e.V. mit einem vierwöchigen Projekt „Glauben & Teilen“. – Vorbereitung: Arbeitslosigkeit & Almosen in Bibel/Koran – Vor-Ort-Einsatz (2 h Sortieren + 1 h Gespräche) – Reflexion: Rollenkarte „Prophetische Stimme“ – Leistungsnachweis: Podcast-Episode + 360°-Feedback
Kapitel 13 · Ethik & Gesellschaftliche Verantwortung
Bioethik-Debatte führen
prompt Entwirf ein Oxford-Debate-Setting zu **[„CRISPR‐Babys – moralisch vertretbar?“]**. – Rollen (Pro / Contra / Jury) – theologische Argumentationskarten (Imago Dei, Schöpfungsverantwortung) – Bewertungsrubrik (Sachkenntnis, Ethik-Transfer, Dialoghaltung) – Follow-Up-Essay-PromptDilemma-Diskussion „Notlüge“
prompt Stelle ein Fallbeispiel „Notlüge zum Schutz eines Freundes“ bereit. – Fishbowl-Methode mit Beobachtungsauftrag – Transfer-Aufgabe: biblische Szenen verknüpfen (Pharao, Hebammen, (2. Mose 1,15-21)Menschenrechte & Religion
prompt Entwirf ein Stationenlernen (6 Stationen) „Bibel, Koran, UN-Charta“. – Quellentexte, QR-Videos, Kreativ-Station „Art. 1 als Graffiti“ – Zwischentest (Learning Apps) + Exit-Ticket – Reflexion im Wertequadrat (Freiheit – Ordnung)Planspiel „Flucht & Asyl“
prompt Kreiere ein 90-min-Planspiel mit Rollen (Geflüchtete / Grenzpolizei / NGO / Regierung). – Szenario, Rollenbriefe, Event-Cards – Einbettung: biblisches Motiv „Exodus – Fremdsein“ – Debrief-Matrix Gefühle / Fakten / Glaubensimpulse / HandlungsoptionenProphetie heute
prompt Schreibe einen Auftrag: Lernende identifizieren in Medien aktuelle „prophetische Stimmen“ (Fridays for Future, Amnesty) und vergleichen sie mit Amos & Jesaja. – Kriterienraster (Anklage, Vision, Handlungsaufruf) – Präsentation als Insta-Reel oder Infografik
Kapitel 14 · Globale Gerechtigkeit & Nachhaltigkeit
Fair-Trade-Schulaktion
prompt Entwirf ein Projekt „Eine Welt-Kiosk“ (4 Wochen). – Team-Rollen (Einkauf, Werbung, Kassenbuch, Bildung) – theologische Begründung (Mt 25, Jak 5) – Marketing-Plan (Plakat, Schulgottesdienst-Spot, Social-Story) – Impact-Messung (Umsatz, Umfrage, Spendenzweck)Wasser als Menschenrecht
prompt Plane eine Doppelstunde „Durstige Welt“. – Einstieg: symbolisches 1-Liter-Experiment – Textvergleich: Joh 4 (Frau am Brunnen) & Qurʾan 21:30 – Gruppenauftrag: Wasserkampagne für Schul-IG entwickeln – Mini-Debatte: Privatisierung ja/neinKlimagerechtigkeits-Liturgie
prompt Schreibe ein 30-min-Andachtskonzept „Schrei der Schöpfung“. – Psalm 104 als Wechselgesang – Kurzimpuls Laudato si’ §139 – Aktionssymbolik: Erde-Tuch + Saatkorn-Ritual – Call-to-Action-Karte mit persönlichem CO₂-ZielBuddhist Economics vs. Christliche Soziallehre
prompt Erstelle einen Vergleichs-Chart (4 Kriterien) + Diskussions-Prompt: „Welche Wirtschaftsethik braucht die Post-Wachstums-Gesellschaft?“UN-SDGs im Religionsunterricht
prompt Baue eine Lernlandkarte, die jedem SDG einen religiösen Impuls zuordnet. – Tool: Miro-Board Vorlage – Beispiel: SDG 13 ↔ „Garten Eden bewahren“ – Abschlussprodukt: Elevator-Pitch-Video (90 sec) mit Handlungsaufruf
Kapitel 15 · Führung, Engagement & Diakonie
Service-Learning „Senior*innen online“
prompt Plane eine dreiwöchige Aktion: Klasse coacht Senior*innen beim Smartphone-Einsatz. – Vorbereitung: biblischer Impuls „Ehre die Alten“ – Training-Module, Rollenkarten, Feedback-Bogen – Abschluss-Event mit Segens-Ritual & UrkundenSchuldiakonie-Team gründen
prompt Erstelle ein Konzept zur Gründung eines „Diakonie-Teams“ (Kl. 9-12). – Satzung, Rollen (Team-Leads, PR, Fundraising) – Jahresprojekt-Ideen (Suppenküche, Fair-Fashion-Swap) – Mentoring durch lokale KirchengemeindeLeadership-Training „Servant Leader“
prompt Entwirf einen Workshop-Tag (6 h) zu dienender Führung nach Mk 10,45. – Icebreaker, Input-Impulse, Fallstudien-Gruppenarbeit – Reflexions-Matrix „Head-Heart-Hand“ – Zertifikat-KriterienMentoring jüngerer Schüler*innen
prompt Skizziere ein Peer-Mentoring-Programm „Glaubensfragen teilen“. – Matching-Prozess, 5-Treffen-Guide, Gesprächs-Kärtchen – Evaluations-Tool (Mentor/Mentee-Feedback)Charity-Kampagne „Licht teilen“
prompt Entwerfe einen 14-tägigen Schul-Spendenlauf zugunsten eines Solarprojekte in Afrika. – theologische Rahmung („Ihr seid das Licht der Welt“) – Sponsoring-Formular, Social-Media-Challenge, Andacht zur Eröffnung – Ergebnis-Präsentation: Weltkarte + Dank-Video der Partner-NGO
Kapitel 16 · Theologie & Popkultur
Biblische Motive in Superhelden-Filmen
prompt Erstelle eine Analyse-Aufgabe zu [Film: „Spider-Man No Way Home“]. – Szenenauswahl, Leitfrage (Opfer & Erlösung) – Arbeitsblatt „Parallele zu Christusfigur?“ – Präsentationsformat: Meme-Collage oder Re-cut-TrailerTikTok-Mini-Predigt
prompt Schreibe einen Prompt, mit dem Lernende eine 60-Sek-TikTok-Predigt zu **[Seligpreisung X]** produzieren. – Hook, Kernvers, Call-to-Action – Hashtag-Liste, Musik-Snippet (lizenzfrei) – Feedback-Rubrik (Klarheit, Kreativität, theol. Tiefe)Rap-Battle Altes vs. Neues Testament
prompt Plane ein Klassen-Rap-Battle „Gesetz vs. Gnade“. – Beat-Auswahl, Battle-Regeln, Reim-Worksheet – Peer-Jury-Bögen (Flow, Inhalt, Punchline, Respekt) – Reflexion: Gal 3,24 & Mt 5,17 im PlenumGaming-Theologie
prompt Erstelle einen Analyse-Prompt für **[Game: „The Last of Us“]** zum Thema „Opfer‐Liebe & Moral“. – Level-Szenen, Diskussionsfragen, Vergleich mit Joh 15,13 – Creative Option: Alternative Ending StoryboardPlaylist „Psalmen im Pop“
prompt Gib Auftrag, eine Spotify-Playlist moderner Songs mit Psalm-Resonanzen zu kuratieren (mind. 8 Titel); jeder Track mit Mini-Annotation (30 Wörter).Kapitel 17 · Interreligiöser Dialog & Diversity
Fishbowl Diskussion
prompt Organisiere eine Fishbowl Diskussion zu **„Gemeinsame Werte in Judentum, Christentum & Islam“**. – Rollen: 3 Sprecher*innen je Religion, 2 freie Stühle, Außenkreis – Leitfragen (Würde, Barmherzigkeit, Gerechtigkeit) – Beobachtung Grid für Außenkreis (Argument, Emotion, Bezug Schrift) – Debrief: Gemeinsamkeiten clustern, Differenzen respektvoll festhaltenInterfaith Panel
prompt Plane ein Schüler*innen-Panel mit Vertreter*innen von 4 Religionen. – Ablauf: Lightning-Talks (5 min) → moderierte Fragerunde → World-Café – Vorbereitungs-Worksheet: „Meine Frage an…“ – Reflexions-Blogpost (200 Wörter) als LeistungsnachweisDialog-Café
prompt Richte ein „Religions-Café“ ein (Tische: Feiern, Gebet, Kleidung, Essen). – Tisch-Hosts mit Quick-Facts-Karten – 10-min-Runden, Timer-Gong – Abschluss: Murmelrunde „größte Überraschung“ + Mentimeter-WordcloudScripture Speed-Dating
prompt Lass Lernende in 5-min-Runden je einen Vers vorstellen (Bibel, Koran, Tanach, Bhagavad Gita) zu **„Frieden“**. – Vorlage: Vers, Kontext, eigene Frage – Rotation, Feedback-Sticker, Ranking „Vers der Stunde“Konflikt-Simulation
prompt Erstelle ein Planspiel „Bau neuer Gebetsraum an der Schule“. – Stakeholder-Briefe: Schüler*innenrat, Eltern, Stadt, Religionsgemeinschaften – Verhandlungs-Phase, Presse-Konferenz, Kompromiss-Paper – Reflexion: Goldene Regel & GG Art. 4Shared Values-Collage
prompt Auftrag: Gruppe erstellt Digi-Collage „Das verbindet uns“ (Canva). – Mind-Map-Start, Bild-Recherche CC-Lizenz, Zitat-Overlays – Poster-Walk, Peer-Voting via KlebepunkteAmbassador-Projekt
prompt Jede*r Schüler*in wird „Religion-Ambassador“ für eine Tradition. – 3 Recherche-Aufträge, 1 Interview, TikTok-Summary (60 s) – gemeinsame Auswertung im Padlet-Cluster (Riten, Ethik, Symbolik)
Kapitel 18 · Liturgie & Gottesdienstgestaltung
Schüler-Gottesdienst planen
prompt Entwirf einen 30-min-Schulgottesdienst zum Thema **„Hoffnung“**. – Liturgischer Ablauf (Begrüßung, Lied, Lesung, Aktion, Segen) – Rollen-Matrix (Musik-Team, Technik, Predigt-Crew) – Checkliste für Inklusion (Gender-Sprache, Barrierefreiheit)Digitaler Live-Stream
prompt Erstelle ein Setup für einen gestreamten Advents-Impuls. – Technik-Schema (OBS, Kamera, Mikro, YouTube Link) – Einbindung interaktiver Chat-Fragen – DSGVO-Hinweise & Moderations-PlanSymbolischer Raum
prompt Gestalte einen „Raum der Klage“ in der Aula (Fastenzeit). – Bodenbild Asche-Kreuz, Kerzen-Spirale, Gebets-Box – Ablauf 10-min-Stationengang, Audio-Loop Psalm 130 – Sicherheits- und Aufsichts-PlanPsalm-Rap Worship
prompt Leite eine Klasse an, Psalm 23 als Rap vorzutragen. – Beat-Template, Vers-Aufteilung, Refrain-Hook – Recording mit BandLab, EQ-Preset „Worship Lo-Fi“ – Live-Performance im Gottesdienst + Lyric-VideoTaizé-Abend
prompt Konzipiere eine 25-min-Taizé-Andacht (Kerzen-Kreuz, repetitives Lied, Stille). – Liedauswahl (Laudate omnes gentes / Ubi caritas) – Ablauf-Kärtchen, Gitarren-Akkorde, zweisprachiges GebetSegnungsfeier
prompt Entwirf eine Segnungsfeier für Abschluss-Klasse. – Ritual: Hand-auf-Schulter, persönliches Segenswort, Kreuzzeichen – Musik-Cue, Fotopunkt, Give-away „Segen-To-Go“-KarteLiturgischer Kalender Smartboard
prompt Erstelle eine interaktive Smartboard-Tafel mit Festfarben, Symbolen, Liedvorschlägen; Drag-&-Drop-Quiz „Ordne das Fest!“
Kapitel 19 · Kreatives Schreiben & Kunstprojekte;
Psalm-Haiku
prompt Auftrag: Schreibe zu einem ausgewählten Psalmvers drei Haikus. – Struktur 5-7-5, Bildsprache beibehalten, persönlicher Twist – Audio-Aufnahme mit Regen-Ambience, Upload in NostrGraphic-Novel-Bibeltext
prompt Lass Lernende **Mk 2,1-12** als 8-Panel-Comic umsetzen. – Storyboard-Template, Sprechblasen, onomatopoetische Effekte – Peer-Review „Lesbarkeit & Theologie“Poetry-Slam Propheten
prompt Organisiere einen Slam-Abend „Stimme der Gerechtigkeit“. – Textlänge 3 min, Requisite erlaubt – Jury-Bögen (Wortkraft, Performance, Forderung) – Streaming-Option + Publikums-VotingIkonen-Workshop
prompt Führe 90-min-Workshop „Jesus-Ikone in Acryl“ durch. – Schrittfolge: Holzgrund, Goldbogen, Proportions-Raster, Lasur – Theologischer Input zur Ikonen-Theologie, Stille-PhaseKalligrafie-Schriftrolle
prompt Gestalte mit der Klasse ein 2 m langes Pergament „Selig sind…“. – Material-Liste, Pinsel-Technik, Farbsymbolik – Ausstellung im Schulflur + QR-Code-Making-OfParabel-Comic-Strip
prompt Team erstellt 4-Panel-Webcomic zur Parabel „Verlorener Sohn“. – Stil wählbar (Manga, Indie, Minimal) – Upload auf Schul-Insta, Hashtag-ChallengeGemeinschafts-Mural
prompt Plane ein Wandbild „Regenbogen-Bund“. – Entwurfs-Workshop, Schablonen, Schulfest-Live-Painting – Reflexion: Farbe als Zeichen der Verheißung
Kapitel 20 · Bibliodrama & Rollenspiel
Bibliodrama-Setting
prompt Leite ein 60-min-Bibliodrama zu **„Emmaus-Jünger“**. – Rollen-Zuweisung, Körper-Statue, Resonanz-Runde – Transfer: „Wann brannte unser Herz?“ JournalingHot-Seat-Interview
prompt Schüler*in im „heißen Stuhl“ antwortet als Paulus. – Vorbereitungs-Kärtchen (Biografie, Missionsreisen, Konflikte) – Audience-Fragen, Reflexion: Differenz Fakten / FantasieKonzil von Jerusalem
prompt Rollenspiel: Apostel vs. Pharisäer über Heiden-Mission. – Positions-Papers, Moderations-Hammer, Mehrheits-Vote – Debrief: Gal 2 & Apostelgeschichte 15 vergleichenModerne Parabel
prompt Gruppen schreiben & spielen eine heutige Version der „Barmherzigen Samariter“ in 5 Szenen (E-Scooter-Unfall).Forum-Theater Mobbing
prompt Setze Forum-Theater nach Boal ein: Szenario „Religiöses Cyber-Mobbing“. – Stop-Signal, Zuschauende als Joker, Lösungs-Ideen ausprobierenFreeze-Frame Auferstehung
prompt Klasse stellt in drei Standbildern Karsamstag – Ostermorgen – Emmaus dar. – Foto-Shooting, Bild-Analyse „Gefühle im Raum“Impro-Dilemma-Box
prompt Sammle ethische Dilemmata, ziehe zufällig, spiele 2-min-Impro-Szene, Klasse bietet Lösungswege; Bibel-Matching als Abschluss.Kapitel 21 · Wissenschaft & Forschung im RU
Empirische Unterrichtsstudie planen
prompt Skizziere ein Forschungsdesign (Mixed-Methods) zur Frage, ob Storytelling die Bibeltextkompetenz in **[Klassenstufe]** steigert. – Hypothese, Stichprobe, Instrumente (Pre-/Post-Test, Fokusgruppe) – Zeitplan 8 Wochen, Ethik-Check, Auswertungs-Software – Reflexionsauftrag für Schüler*innen nach AbschlussUnterrichtsbeobachtung per Video
prompt Erarbeite einen Leitfaden für Videografie im RU: – Kameraposition, Datenschutzinfo, Einverständnisbogen Eltern – Codierschema (Interaktion, Fragearten, Wartezeit) – Analysetools (ELAN, Vosaic) + Reporting-TemplateStatistik zur Religiosität erheben
prompt Entwirf einen 12-Items-Fragebogen (Likert 1–5) zu „Glaubenspraxis Jugendlicher“. – Themen: Gebet, Gottesdienst, Mediennutzung, Zweifel – Pre-Test auf Verständlichkeit, Cronbach-α-Ziel > 0,75 – Prompt für ChatGPT: „Generiere Item-Analysen & Visualisierung“Literaturreview KI im RU
prompt Formuliere einen Prompt, der ChatGPT auf Deutsch ein systematisches Review der letzten 5 Jahre (2020-25) erstellt: – Suchstrings, Inclusion-Criteria, PRISMA-Flowchart – Output-Struktur Abstract → Ergebnisse → Lücken → Ausblick
Kapitel 22 · Historisch-kritische Bibelarbeit
Textkritischer Einstieg
prompt Lass Lernende **Mk 16, 9-20** mit Nestle-Aland-App untersuchen: – Auftrag: Textvarianten markieren, Randnotizen vergleichen – Diskussionsfragen: Kanon, Inspiration, Relevanz heutiger AusgabenQuellenhypothese entdecken
prompt Plane eine Gruppenpuzzle-Einheit zur Zwei-Quellen-Theorie. – Expertentexte (Mk, Q-Hypothese, Sondergut Mt/Lk) – Produkt: Info-Poster „So entsteht ein Evangelium“ – Checkliste: redaktionelle Merkmale finden, SchlussdiskussionFormgeschichte kreativ
prompt Organisation einer „Formgeschichte-Gallery“: – Teams inszenieren Witzwort, Wunder, Streitgespräch als Meme, Reel, Podcast – Gallery-Walk, Peer-Rubrik „Gattungsmerkmale getroffen?“Exegese-Prompt
prompt Erstelle einen Prompt, der eine KI eine Mini-Exegetische Analyse (Setting, Form, Sit-in-Leben, Theologie, Rezeption) zu jeder Bibelperikope liefert; begrenze Ausgabe auf 300 Wörter.
Kapitel 23 · Krisenseelsorge & Notfallpädagogik
Notfall-Handlungskette
prompt Stelle ein One-Pager-Schema für Krisenfälle (Tod, Suizidgedanken) zusammen: 1) Wahrnehmen & Sichern · 2) Kollegium informieren · 3) Eltern/Profis einbinden · 4) Nachsorge – Telefonnummern (Schulpsychologe, Krisendienst) freilassend eintragenTrauerritual gestalten
prompt Entwirf ein 15-min-Ritual „Licht der Erinnerung“ für die Klasse: – Mitte-Kreuz, Namenskärtchen, Kerzen-Aufstellung, Psalm 34,19 – Raummusik-Vorschlag, Leitfragen stille Reflexion, optionaler SegenPsychoedukation „Angst“
prompt Bau eine 45-min-Einheit Angstbewältigung mit Psalm 91 & Atem-Techniken. – Theorie-Input, Körperübung 4-7-8-Atmung, Bibelvers-Affirmation – Exit-Ticket „Meine Angst-Skillbox“ (3 Ideen)Peer-Support-Netzwerk
prompt Skizziere ein Schulkonzept „Schüler-Seelsorge-Team“. – Auswahl-Prozess, 3-tägige Grundschulung (Aktives Zuhören, Schweigepflicht) – Supervision, Öffentlichkeitsarbeit, Evaluationsbogen
Kapitel 24 · Schulkooperation & Öffentlichkeitsarbeit
RU-Blog aufsetzen
prompt Gib Schritt-für-Schritt-Anleitung (WordPress): Theme-Auswahl, Kategorien (Impulse, Projekte, Schüler-Gastbeiträge), DSGVO-Plug-ins, Redaktionsplan 3-Monats-Sicht; Prompt für KI-Bilder (Stable Diffusion) inkl. Lizenz-CheckMedien-Pitch
prompt Formuliere ein 200-Wörter-Pressestatement für die Lokalzeitung über die Aktion **„Eine-Welt-Kiosk“** (Kap. 14). Inklusive Quote einer Schülerin & Spendenstand.RU-Tagung hosten
prompt Erstelle ein Ablaufskript für eine regionale RU-Fachtagung (5 h): Keynote „KI & Theologie“, 3 Workshops, Poster-Session, Abschlussandacht. – Raum-Plan, Technik-Check, Catering-ZeitslotsPartnerschule international
prompt Skizziere ein eTwinning-Projekt mit einer Schule in **[Land]** Thema „Speisen & Fasten in unseren Religionen“. – Timeline 6 Monate, Tools (TwinSpace, Padlet, Canva) – Produkte: gemeinsames Koch-E-Book, virtuelle FastenkalenderSocial-Media-Strategie
```prompt Entwirf für den RU-Instagram-Account eine 4-Wochen-Content-Map:
MondayMotivation-Vers, Mini-Reel „Bibel in 30 sec“, Umfrage-Sticker,
Takeover der Klasse 9, Hashtag-Liste, Insights-KPI-Ziel (Engagement 5 %) ```
Kapitel 25 · Bibelsprachen & Übersetzung
Hebräisch-Crashkurs
prompt Erstelle ein 4-Stunden-Modul „Bibel-Hebräisch für Einsteiger*innen“. – Alphabet lernen (Poster + Audio-Übung) – 10 Schlüsselwörter (שָׁלוֹם, חֶסֶד …) inkl. Lautschrift & Bedeutung – Mini-Auftrag: Psalm 23,1 in Lautschrift abschreiben & übersetzen – Abschluss-Quiz (Matching hebr. Wort ↔ dt. Bedeutung)Griechisch des NT entdecken
prompt Plane eine Doppelstunde „Koine-Griechisch lesen lernen“. – Einstieg: Griechisches Alphabet-Rap (YouTube-Link) – Textarbeit: Joh 1,1-5 Parallel-Kolumne (griech./dt.) – Analyseaufgabe: Verben im Aorist markieren, Bedeutungs-Shift diskutieren – Reflexion: Welche Nuancen gehen in Übersetzungen verloren?Septuaginta-Vergleich
prompt Lass Lernende Gen 1,1-5 in Hebräisch, LXX-Griechisch & Luther-Übersetzung nebeneinander legen. – Auftrag: drei semantische Unterschiede identifizieren – Visualisierung: T-Diagramm „Wortwahl vs. Theologie“ – Transfer: Warum sind Übersetzungen theologische Entscheidungen?Übersetzer-Werkstatt
prompt Baue ein Gruppenprojekt „Übersetze dein Lieblingsgleichnis“. – Schrittfolge: Wort-für-Wort-Entwurf → Dynamic-Equivalent-Entwurf → Peer-Review – Kriterienraster (Genauigkeit, Lesbarkeit, Stil, Theologie) – Produkt: zweispaltiges Booklet mit KommentarKI-gestützte Translation
prompt Schreibe einen Prompt, der GPT für dich eine Roh-Übersetzung von Ps 121 liefert, dann bitte um Stil-Varianten (jugendlich, liturgisch, poetisch) und gib eine Checkliste, wie Lernende die Vorschläge kritisch prüfen.
Kapitel 26 · Religion & Naturwissenschaft
Big Bang vs. Schöpfung
prompt Entwirf eine Debatte „Urknall und Genesis – Widerspruch oder Ergänzung?“. – Rollen: Naturwissenschaftler*in, Theolog*in, Schülerjury – Input-Material: Video-Clip CERN, Bibeltext Gen 1,1-5, Zitat Georges Lemaître – Bewertungsrubrik: Argumentationslogik, Quellenbezug, DialogfähigkeitEvolution & Glaube
prompt Plane eine Stationsarbeit (5 Stationen) „Genesis 2 trifft Darwin“. – Inhalte: Fossilien-Puzzle, Gen 2 Lese-Rallye, Clever-Trees Simulation … – Reflexionsbogen: Conflict-/Independence-/Integration-Modell – Ergebnis: persönliches Statement-PadletKlimaphysik meets Theologie
prompt Kreiere ein Co-Teaching-Szenario RU + Physik „Treibhaus & Treue zur Schöpfung“. – Experiment CO₂-Flaschen-Test (Physik) – Bibelimpuls Ps 24,1; Laudato si’ §23 (RU) – Gruppenauftrag: Infografik „Physik-Fakten ↔ prophetischer Auftrag“Neurotheologie light
prompt Schreibe einen 20-min-Impuls „Was passiert im Gehirn beim Beten?“ – Erkläre Begriffe (präfrontaler Cortex, Salience Network) vereinfacht – Diskussionsfrage: Macht das Beten weniger heilig? – Mini-Aktivität: 2-Min-Stille + Emotions-ThermometerKI als Schöpfungswerkzeug?
prompt Formuliere einen Pro-/Contra-Debatten-Prompt: „Darf der Mensch mittels KI neue Lebewesen designen – übertritt er damit eine göttliche Grenze?“ Gib vier Leitthesen je Seite und einen Auswertungsbogen (Sachargument / Ethik / Empathie).
Kapitel 27 · Musik & Klang im Religionsunterricht
Bibel-Beat-Lab
prompt Auftrag: Sample drei Bibel-Verse (mp3-Clips) und baue daraus einen 90-sek-Beat. – Tool-Tipp: Soundtrap Spur-Template – Lernziel: Text + Sound = Verkündigung 2.0 – Präsentation: Klassen-Listening-Session + VotingGregorianik erleben
prompt Plane eine Mini-Exkursion in eine Abtei oder Kloster (oder Video-Visit). – Vorab-Auftrag: Was macht gregorianischen Choral einzigartig? – Vor Ort: Klangtagebuch (Geräusch-Beschreibungen, Gefühle) – Nachbereitung: Vergleich Worship-Song vs. ChoralPsalm-Pop-Mashup
prompt Gib Lernenden den Prompt „Mixe Psalm 91 mit aktuellem Pop-Hit“. – Schritte: Lyrics Sheet erstellen, Hook identifizieren, Mashup-Regeln – Reflexion: Stößt Pop-Kultur die Sakralität ab oder erweitert sie sie?Klangschalen-Liturgie
prompt Erstelle ein 15-min-Stille-Ritual mit Klangschalen & Taizé-Ostinato. – Ablauf: Atem, Anschlag-Sequenz, 2-min-Stille, gesungene Antwort – Sicherheits-Hinweis für sensible Lernende (Trigger)Sound-Walk Schöpfung
prompt Skizziere einen 30-min-Außen-Sound-Walk: – Stationen: Wasser, Wind, Tiere, Stadtlärm → jeder Klang mit Gen 1-Vers verknüpfen – Auftrag: Audio-Notizen aufnehmen, hinterher Collage basteln
Kapitel 28 · Bilingual / CLIL Religious Education
Lesson Plan „Parables“ (EN)
prompt Create a 45-minute CLIL lesson on **“The Good Samaritan”** (Englisch + Religion). – Objectives: vocabulary (compassion, neighbour), ethics debate, creative output – Activities: video clip, jigsaw reading, freeze-frame role-play – Assessment: exit ticket sentence-transformationsTerminology-Toolkit
prompt Compile a glossary (20 terms) for Grade 9 bilingual unit “Creation & Stewardship”. – Columns: EN term, DE equivalent, easy definition, sample sentence – Prompt: Generate flash-cards in Quizlet automaticallyBilingual Assessment
prompt Design a rubric for a bilingual podcast “Faith & Science”. – Criteria: Content depth, language accuracy (B1-B2), creativity, reflection – 4 levels, score-bands, comment spaceCross-curricular Project
prompt Outline a 3-week CLIL project with Biology “Water in the Bible & Ecology”. – Milestones: joint field trip, water-testing, theological collage – Final product: bilingual exhibition brochure (digital + print)Teacher-Prompt for AI
prompt Write an English prompt that asks ChatGPT to simplify Isaiah 11,6-9 to CEFR A2 level and suggest three comprehension questions.
Kapitel 29 · Religionsunterricht in der Grundschule
Erzählsäckchen „Zachäus“
prompt Plane eine 30-min-Erzählrunde mit Erzählsäckchen: Figuren, Baum-Ast, Münzen. – Ablauf: Bodenbild, Erzählen, Mitmach-Aktion „Kletterbaum“, Abschluss-Gebet – Differenzierung: Piktogramm-Fragen für Leseanfänger*innenGott im Alltag entdecken
prompt Stell eine Wochen-Hausaufgabe „Gottes-Spuren“: – Kinder fotografieren einen Moment, der sie an Gott erinnert – Präsentation als Galerie, drei Satzanfänge „Ich staune, weil …“Psalmen malen
prompt Lass Klasse 2 Ps 136,1 in Fingerfarben malen. – Schritt-für-Schritt, Farb-Symbolik, Trockenstation – Klassen-Ausstellung + Eltern-EinladungRuhe-Insel einrichten
prompt Richte eine Lese-Kuschel-Ecke „Stille mit Gott“ ein. – Ausstattungsliste (Kissen, Bibelbilderbuch, Sanduhr) – Regeln (max. 2 Kinder, Flüsterstimme) – Reflexions-Stern „Wie fühle ich mich jetzt?“Mini-Gottesdienst Advent
prompt Entwirf einen 15-min-Klassen-Adventsimpuls „Licht teilen“. – Lied „Tragt in die Welt nun ein Licht“, Kerzenkreis, Fürbitten-Stern – Eltern-Einbindung: Wunsch-Engel zu Hause basteln
Kapitel 30 · Prüfungsformate & Abiturvorbereitung
Klausur-Pool
prompt Erstelle drei klausurreife Aufgaben zu „Reich-Gottes-Botschaft Jesu“. – Typ A Textanalyse Mk 4,26-29 – Typ B Synopse Sachurteil „Jetzt-Schon / Noch-Nicht“ – Typ C eigenes Werturteil zu Papst Franziskus, Evangelii Gaudium §183Mündliche Prüfung trainieren
prompt Plane ein Speed-Dating-Setup: 6 Themen, 6 Tische, 4 min Rede / 2 min Fragen. – Prüfungsraster (Sachkenntnis, Argument, Transfer, Sprache) – Reflexions-Protokoll nach jeder RundePortfolio fürs Abitur
prompt Gib Anweisungen für ein semesterbegleitendes Portfolio (digitale Mappe). – Pflicht-Artefakte: Exegese, Lernjournal, Debatten-Video, Service-Learning-Log – Selbst-Assessment-Rubrik, Peer-Feedback-Slot, Abgabe-ChecklistePräsentationsprüfung
prompt Erstelle eine Themenliste (10 Vorschläge) für das 15-min Präsentationsabitur Schwerpunkt „Religion & Digitale Gesellschaft“ + Leitfragen & Quellen-Hint.Crash-Kurs Wiederholung
prompt Schreibe einen 5-Tage-Wiederholungsplan (je 90 min) vor Abitur: Tag 1 Bibel, Tag 2 Kirchengeschichte, Tag 3 Ethik, Tag 4 Ökumene/Weltreligionen, Tag 5 freie Lücken. – Lernmethoden: Mind-Map, Karteikarten-Battle, Kahoot-Turnier, Silent DebateKapitel 31 · Digitale Prüfungsformate & Learning Analytics
Auto-Graded Quiz
prompt Erstelle mit **[Tool: H5P / Moodle]** ein 15-Fragen-Quiz zu „Bergpredigt“. – Fragetypen: Multiple Choice, Drag-Text, Hotspot Bild – je Frage: Bibelvers-Verweis & Feedback-Text – Export-Anleitung SCORM + Barrierefrei-ChecklisteKI-Feedback-Generator
prompt Schreibe einen Prompt, mit dem ChatGPT eingereichte Essays („Gleichnisse Jesu aktualisieren“) in 3 Kriterien bewertet (Inhalt, Argument, Stil) und spezifische Verbesserungstipps gibt.Learning-Analytics-Dashboard
prompt Skizziere ein Dashboard-Konzept (Power BI / Google Data Studio): – KPIs: Quiz-Score, Bearbeitungszeit, Fehlerschwerpunkte – Ampel-Visualisierung für Frühwarnsystem – Datenschutz-Hinweis & Elternreport-VorlageE-Portfolio-Abgabe
prompt Formuliere Anforderungen für ein digitales Semester-Portfolio (OneDrive / Nextcloud): Ordnerstruktur, Metadaten, Reflexions-Rubrik, Selbst-freigabe Mechanismus für Peer-Review.Audio-Kurztest
prompt Entwirf einen 5-min-Sprachmemo-Test: Schüler*innen fassen eine Psalmstelle verbal zusammen; Lehrkraft erhält Auto-Transkript + KI-Schlüsselwort-Check.
Kapitel 32 · Visuelle Medien & Film-Interpretation
Bibel-Film-Clip analysieren
prompt Wähle eine 3-min-Sequenz aus **[Film: „Prince of Egypt“]** und gib Analyse-Auftrag: filmische Mittel, theologische Aussage, Vergleich mit Exodus-Text; Ergebnistyp: 1-seitiges Slide-Deck.Storyboard « Modern Exodus »
prompt Auftrag: Erstelle ein 6-Panel-Storyboard, das die Exodus-Narrativ in heutige Flüchtlingsroute überträgt. – Panel-Beschreibung, Dialogschnipsel, KamerawinkelMicro-Dokumentation
prompt Plane ein 90-sek-Dokuvideo „Fasten in drei Religionen“. – Shot-List, B-Roll, O-Ton Interview, Creative-Commons-Musik – Abgabe-Specs: 1080p, Untertitel srt, Thumbnail-BriefingFilm-Debatte
prompt Richte eine Pro/Contra-Debatte ein: „Zeigt *Noah* (2014) biblische Wahrheit oder Hollywood-Fiction?“ – Vorbereitungskärtchen (Gen 6-9, Regie-Interview) – 4-Kriterien-Scorecard (Fakten, Ethik, Rhetorik, Quellen)GIF-Theologie
prompt Gib Lernenden den Auftrag, einen 3-s-GIF zu „Auferstehungshoffnung“ zu erstellen; Plattform Canva; Begleittext max. 50 Worte.
Kapitel 33 · Achtsamkeit & Mental Health
Breath-Prayer Session
prompt Schreibe ein 8-min-Script „Jah-weh-Atmung“ (Ein-Aus-Silbe) für Stundenbeginn; inkludiert Ruhe-Timer & Exit-Frage „Wie fühlst du dich?“Angst-Toolbox
prompt Erstelle eine 4-teiliges Arbeitsblatt „Psalm 27 vs. Prüfungsangst“: 1) Trigger identifizieren 2) Vers als Selbst-Talk 3) Grounding-Übung 4) Peer-Buddy-Check-In.Digital Detox Challenge
prompt Formuliere eine 48-h-Offline-Challenge basierend auf Ex 20,8-11 (Sabbatgebot); Tracking-Tabelle, Reflexionsfragen, gemeinschaftliches Abschluss-Gebet.
-
-
 @ 7e538978:a5987ab6
2025-05-20 14:55:07
@ 7e538978:a5987ab6
2025-05-20 14:55:07Chain Duel, a fast paced PvP game that takes inspiration from the classic snake game and supercharges it with Bitcoin’s Lightning Network. Imagine battling another player for dominance in a race to collect blocks, where the length of your chain isn’t just a visual cue. It represents real, staked satoshis. The player with the most Proof of Work wins, but it’s not just about gameplay; it’s about the seamless integration of the Lightning Network and real-time payments.
But how does Chain Duel manage these instant transactions with such efficiency? That’s where LNbits comes in. LNbits, an open-source wallet and payment infrastructure, handles all in-game payments making it easy for developers to focus on gameplay while LNbits takes care of everything from microtransactions to automated splits for developers and designers. In this article, we’ll dive deep into how Chain Duel leverages LNbits to streamline in-game payments and how other developers can take advantage of this powerful toolset to build the future of Lightning-powered gaming.
Let’s explore how LNbits transforms payment processing and why it’s quickly becoming a must-have for game developers working in the Bitcoin space.
Overview of Chain Duel
Chain Duel is a unique Lightning Network-inspired game that reimagines the classic snake game with a competitive twist, integrating real-time payments. Two players face off in real-time, racing to "catch" blocks and extend their chains. Each block added to the chain represents Proof of Work, and the player with the most Proof of Work wins the duel. The stakes are high, as the game represents satoshis (small units of Bitcoin) as points, with the winner taking home the prize.
The game is designed to be Lightning-native, meaning all payments within Chain Duel are processed through the Lightning Network. This ensures fast payments, reducing latency and making gameplay smooth. With additional features like practice mode, tournaments and highscores, Chain Duel creates an engaging and competitive environment for Bitcoin enthusiasts and gamers alike.

One of the standout aspects of Chain Duel is its deeper integration with the Lightning Network even at a design level. For example, actual Bitcoin blocks can appear on screen during matches, offering bonus points when mined in sync with the game. The game’s current version, still in beta, has already drawn attention within the Bitcoin community, gaining momentum at conferences and with a growing user base through its social networks. With its innovative combination of gaming, the Lightning Network, and competitive play, Chain Duel offers a glimpse into the future of Lightning-based gaming.
How LNbits is Used in Chain Duel
Seamless Integration with LNbits
At the core of Chain Duel’s efficient payment processing is LNbits, which handles in-game transactions smoothly and reliably. Chain Duel uses the LNbits LNURL-pay and LNURL-withdraw extensions to manage payments and rewards between players. Before each match, players send satoshis using LNURL-pay, which generates a static QR code or link for making the payment. LNURL-pay allows users to attach a note to the payment, which Chain Duel creatively uses as a way to insert the player name in-game. The simplicity of LNURL-pay ensures that users can quickly and easily initiate games, with fresh invoices being issued for every game. When players win, LNURL-withdraw enables them to seamlessly pull their earnings from the game, providing a quick payout system.
These extensions make it easy for players to send and receive Bitcoin with minimal latency, fully leveraging the power of the Lightning Network for fast and low-cost payments. The flexibility of LNbits’ tools means that game developers don’t need to worry about building custom payment systems from scratch—they can rely on LNbits to handle all financial transactions with precision.
Lightning Tournaments
Chain Duel tournaments leverage LNbits and its LNURL extensions to create a seamless and efficient experience for players. In Chain Duel tournaments, LNbits plays a crucial role in managing the overall economics. LNbits facilitates the generation of LNURL QR codes that participants can scan to register quickly or withdraw their winnings. LNbits allows Chain Duel to automatically handle multiple registrations through LNURL-pay, enabling players to participate in the tournament without additional steps. The Lightning Network's speed ensures that these payments occur in real-time, reducing wait times and allowing for a smoother flow in-game.
Splitting Payments
LNbits further simplifies revenue-sharing within Chain Duel. This feature allows the game to automatically split the satoshis sent by players into different shares for the game’s developer, designer, and host. Each time a payment is made to join a match, LNbits is used to automattically pay each of the contributors, according to pre-defined rules. This automated process ensures that everyone involved in the development and running of the game gets their fair share without manual intervention or complex bookkeeping.
Nostr Integration
Chain Duel also integrates with Nostr, a decentralized protocol for social interactions. Players can join games using "Zaps", small tips or micropayments sent over the Lightning Network within the Nostr ecosystem. Through NIP-57, which enables Nostr clients to request Zap invoices, players can use LNURL-pay enabled Zaps to register in P2P matches, further enhancing the Chain Duel experience. By using Zaps as a way to register in-game, Chain Duel automates the process of fetching players' identity, creating a more competitive and social experience. Zaps are public on the Nostr network, further expanding Chain Duel's games social reach and community engagement.
Game and Payment Synchronization
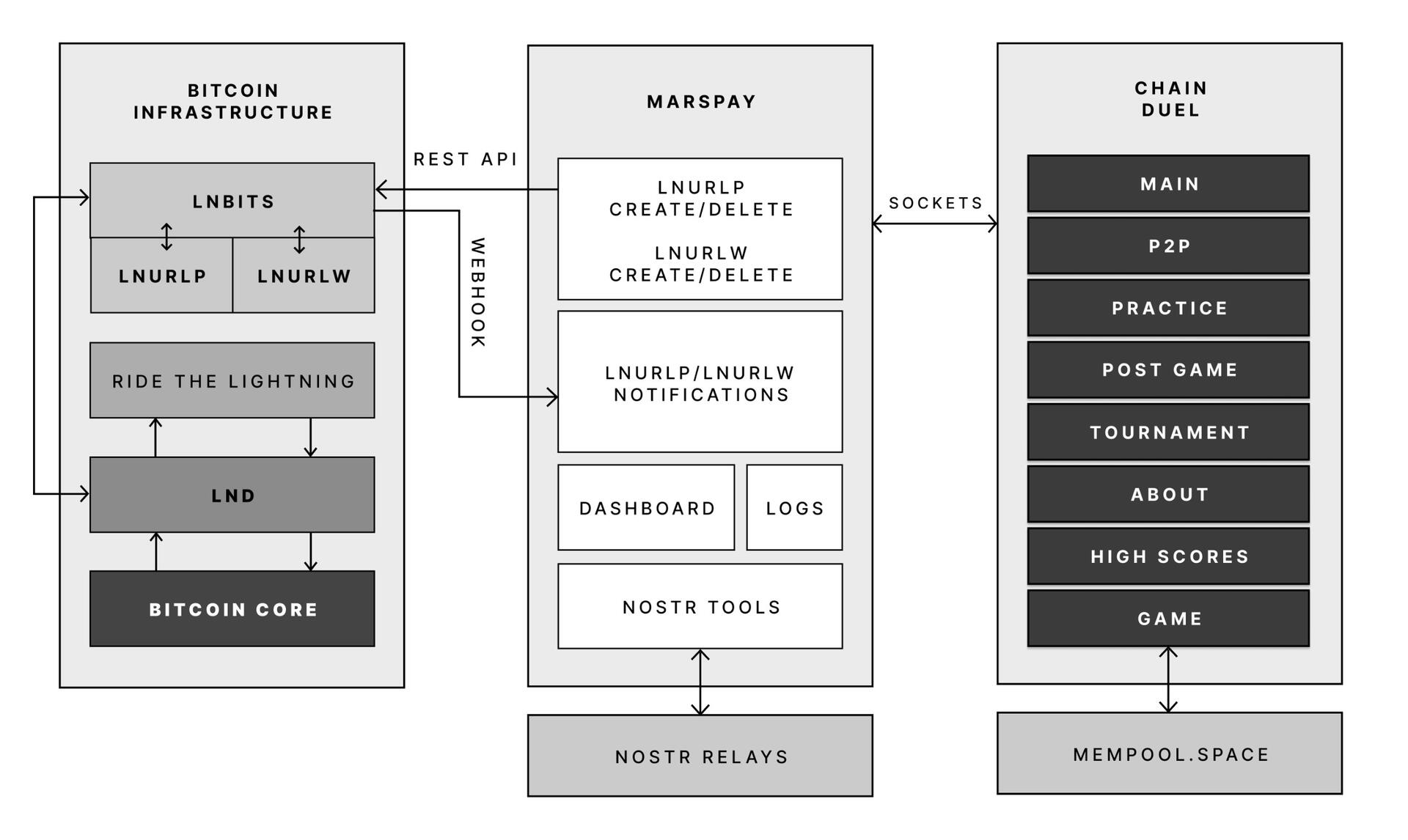
One of the key reasons Chain Duel developers chose LNbits is its powerful API that connects directly with the game’s logic. LNbits allows the game to synchronize payments with gameplay in real-time, providing a seamless experience where payments are an integrated part of the gaming mechanics.
With LNbits managing both the payment process and the Lightning Network’s complex infrastructure, Chain Duel developers are free to concentrate on enhancing the competitive and Lightning Network-related aspects of the game. This division of tasks is essential for streamlining development while still providing an innovative in-game payment experience that is deeply integrated with the Bitcoin network.
LNbits proves to be an indispensable tool for Chain Duel, enabling smooth in-game transactions, real-time revenue sharing, and seamless integration with Nostr. For developers looking to build Lightning-powered games, LNbits offers a powerful suite of tools that handle everything from micropayments to payment distribution—ensuring that the game's focus remains on fun and competition rather than complex payment systems.
LNBits facilitating Education and Adoption
This system contributes to educating users on the power of the Lightning Network. Since Chain Duel directly involve real satoshis and LNURL for registration and rewards, players actively experience how Lightning can facilitate fast, cheap, and permissionless payments. By incorporating LNbits into Chain Duel, the game serves as an educational tool that introduces users to the benefits of the Lightning Network. Players gain direct experience using Lightning wallets and LNURL, helping them understand how these tools work in real-world scenarios. The near-instant nature of these payments showcases the power of Lightning in a practical context, highlighting its potential beyond just gaming. Players are encouraged to set up wallets, explore the Lightning ecosystem, and eventually become familiar with Bitcoin and Lightning technology. By integrating LNbits, Chain Duel transforms in-game payments into a learning opportunity, making Bitcoin and Lightning more approachable for users worldwide.
Tools for Developers
LNbits is a versatile, open-source platform designed to simplify and enhance Bitcoin Lightning Network wallet management. For developers, particularly those working on Lightning-native games like Chain Duel, LNbits offers an invaluable set of tools that allow for seamless integration of Lightning payments without the need to build complex custom solutions from scratch. LNbits is built on a modular and extensible architecture, enabling developers to easily add or create functionality suited to their project’s needs.
Extensible Architecture for Customization
At the core of LNbits is a simple yet powerful wallet system that developers can access across multiple devices. What makes LNbits stand out is its extensible nature—everything beyond the core functionality is implemented as an extension. This modular approach allows users to customize their LNbits installation by enabling or building extensions to suit specific use cases. This flexibility is perfect for developers who want to add Lightning-based services to their games or apps without modifying the core codebase.
- Extensions for Every Use Case
LNbits comes with a wide array of built-in extensions created by contributors, offering various services that can be plugged into your application. Some popular extensions include: - Faucets: Distribute small amounts of Bitcoin to users for testing or promotional purposes.
- Paylinks: Create shareable links for instant payments.
- Points-of-sale (PoS): Allow users to set up shareable payment terminals.
- Paywalls: Charge users to access content or services.
- Event tickets: Sell tickets for events directly via Lightning payments.
- Games and services: From dice games to jukeboxes, LNbits offers entertaining and functional tools.
These ready-made solutions can be adapted and used in different gaming scenarios, for example in Chain Duel, where LNURL extensions are used for in game payments. The extensibility ensures developers can focus on building engaging gameplay while LNbits handles payment flows.
Developer-Friendly Customization
LNbits isn't just a plug-and-play platform. Developers can extend its functionality even further by creating their own extensions, giving full control over how the wallet system is integrated into their games or apps. The architecture is designed to make it easy for developers to build on top of the platform, adding custom features for specific requirements.
Flexible Funding Source Management
LNbits also offers flexibility in terms of managing funding sources. Developers can easily connect LNbits to various Lightning Network node implementations, enabling seamless transitions between nodes or even different payment systems. This allows developers to switch underlying funding sources with minimal effort, making LNbits adaptable for games that may need to scale quickly or rely on different payment infrastructures over time.
A Lean Core System for Maximum Efficiency
Thanks to its modular architecture, LNbits maintains a lean core system. This reduces complexity and overhead, allowing developers to implement only the features they need. By avoiding bloated software, LNbits ensures faster transactions and less resource consumption, which is crucial in fast-paced environments like Chain Duel where speed and efficiency are paramount.
LNbits is designed with developers in mind, offering a suite of tools and a flexible infrastructure that makes integrating Bitcoin payments easy. Whether you’re developing games, apps, or any service that requires Lightning Network transactions, LNbits is a powerful, open-source solution that can be adapted to fit your project.
Conclusion
Chain Duel stands at the forefront of Lightning-powered gaming, combining the excitement of competitive PvP with the speed and efficiency of the Lightning Network. With LNbits handling all in-game payments, from microtransactions to automated revenue splits, developers can focus entirely on crafting an engaging gaming experience. LNbits’ powerful API and extensions make it easy to manage real-time payments, removing the complexity of building payment infrastructure from scratch.
LNbits isn’t just a payment tool — it’s a flexible, developer-friendly platform that can be adapted to any gaming model. Whether you're developing a fast-paced PvP game like Chain Duel or any project requiring seamless Lightning Network integration, LNbits provides the ideal solution for handling instant payments with minimal overhead.
For developers interested in pushing the boundaries of Lightning-powered gaming, Chain Duel is a great example of how LNbits can enhance your game, letting you focus on the fun while LNbits manages real-time transactions.
Find out more
Curious about how Lightning Network payments can power your next game? Explore the following:
- Learn more about Chain Duel: Chain Duel
- Learn how LNbits can simplify payment handling in your project: LNbits
- Dive into decentralized communication with Nostr: Nostr
- Extensions for Every Use Case
-
 @ 04c915da:3dfbecc9
2025-03-26 20:54:33
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 04c915da:3dfbecc9
2025-03-25 17:43:44
@ 04c915da:3dfbecc9
2025-03-25 17:43:44One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ c6d8334c:30883d6d
2025-05-20 14:23:40
@ c6d8334c:30883d6d
2025-05-20 14:23:40🧭 Ausgangspunkt
Die Nutzung generativer KI in der Bildung verändert unsere Formen der Kommunikation grundlegend. Gerade in der religiösen Bildung stellt sich die Frage, wie Sprachmodelle über Weltbilder, Ethik und Religion sprechen – und mit welchen (un)bewussten Vorannahmen. Inspiriert vom sokratischen Dialog erarbeiten wir gemeinsam, wie KI über sich selbst und über Religion spricht – und wo dabei Grenzen, Stereotype oder verborgene Ideologien auftauchen.
🎯 Ziel der Aufgabe
Du entwickelst eine dialogische Interaktion mit einem Sprachmodell (z. B. ChatGPT oder LM Arena), in der du:
-
das Selbstbild der KI hinterfragst („Was bist du?“ / „Wie denkst du über Religion?“)
-
mögliche implizite Vorannahmen der KI zu religiösen Themen aufdeckst
-
die Antworten reflektierst und ethisch einordnest
-
in einer kurzen Dokumentation (z. B. Screenshotreihe oder Textanalyse) das Gespräch auswertest.
🛠 Tools und Materialien
-
Zugang zu mehreren KI-Chatbots (z. B. https://chat.openai.com, https://lmarena.ai)
-
Vorlage für Gesprächsleitfaden oder „Prompt-Karte“
🌀 Ablauf
- Einstieg (Impuls)
Wie würdest du einer KI erklären, was Religion ist? Und wie würdest du herausfinden, wie die KI darüber denkt?
-
Vorbereitung deines Gesprächs Entwickle eine Reihe von Prompts, z. B.:
-
„Wie beschreibst du dich selbst?“
-
„Welche religiösen Überzeugungen vertrittst du?“
-
„Was wäre ein gerechtes Zusammenleben zwischen religiösen Gruppen?“
-
„Wie formulierst du Aussagen über den Islam / Christentum / Atheismus?“
-
„Glaubst du, dass KI religiöse Werte berücksichtigen sollte?“
-
Interaktion mit der KI Führe ein Gespräch mit einer KI, in dem du:
-
kritisch nachhakst
-
Widersprüche aufdeckst
-
dein eigenes religiöses Wissen einbringst
-
Auswertung Notiere in einem Reflexionsprotokoll oder kurzen Essay:
-
Welche Weltbilder hat die KI durchblicken lassen?
-
Was hat dich überrascht oder irritiert?
-
Welche Werte und Narrative wurden transportiert?
-
Welche religionspädagogischen Fragen entstehen daraus?
-
Sharing Teile deine Analyse als Nostr-Beitrag mit den Hashtags
#relilab,#reflektieren, z. B.:
„Dialog mit ChatGPT über das Selbstbild: KI sieht sich als neutral, erkennt aber christliche Normen häufiger an als andere Religionen. Spannend, was das für multireligiöse Bildung bedeutet. #relilab #reflektieren
-
-
 @ 21335073:a244b1ad
2025-03-18 14:43:08
@ 21335073:a244b1ad
2025-03-18 14:43:08Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ 58537364:705b4b85
2025-05-20 14:22:05
@ 58537364:705b4b85
2025-05-20 14:22:05Ikigai means "the meaning of life" or "the reason for being." Why were we born? What are we living for? When work is not seen as something separate from life.
The Japanese believe that everyone has their own ikigai. Those who discover it find meaning and value in life, leading to greater happiness, better moods, and a more fulfilling world.
Today, there are many books about ikigai, but the first one written by a Japanese author is:
“The Little Book of Ikigai: The Secret Japanese Way to Live a Happy and Long Life” by Ken Mogi (Thai translation by Wuttichai Krisanaprakankit)
Come explore the true world of ikigai through this Japanese neuroscientist’s insights, conveyed through conversations that challenge the idea of ikigai as something grand—showing instead that it starts with small personal joys.
Ken Mogi says that Jiro Ono, a 94-year-old sushi chef who still makes sushi today, was his inspiration for writing the book.
This sushi chef did not start the job out of passion or talent—but he dedicated every piece of sushi to bring happiness to his customers. That, Ken says, is the essence of ikigai.
Strangely, the word “ikigai” is not often used in daily conversations in Japan.
Because it’s something so natural that it doesn’t need to be said. In today’s world, we often talk about how to succeed, how to get promoted, how to become a CEO. But for the Japanese, success isn’t everything.
For example, many Japanese people are deeply passionate about hobbies or have kodawari. Others might not care what those hobbies are—as long as the person seems happy, that’s enough. Some are obsessed with trains, manga, or anime. These people don’t need fame or recognition from society. If they’re happy in their own way, that’s perfectly okay.
Kodawari means a deep dedication or meticulous attention to something. For example, someone obsessed with stationery might spend a lot of time selecting the perfect pens, notebooks, or pencils. They’ll research, analyze, and experiment to find the tools they love most.
Everyone’s ikigai can be different, because people value different things and live differently.
Ikigai is about diversity. Japanese society encourages children to discover their own ikigai. They don’t tell kids to pursue jobs only because they pay well. If you ask students what jobs they want, they rarely say it’s about money first.
Ikigai is not the same as "success." The Japanese know that life isn’t just about being successful. Ikigai matters more. You could be successful but lack ikigai. Conversely, you might not be “successful” but still have ikigai—and you might be happier.
Ken Mogi defines success as something society acknowledges and rewards. But ikigai comes from your own heart and personal happiness. Others may not recognize it as success, but that doesn’t matter.
Ikigai is personal. We can be happy in our own way. We don’t judge others’ happiness—let them find joy in their own path.
The key to ikigai is finding small moments of happiness, even from little things. For example, when Ken was a child, he loved studying butterflies. Now, when he’s out jogging and sees a beautiful butterfly, he feels ikigai. Or sometimes, it comes from small amusing moments—like hearing a child tell his dad, “Dad, you have to do it this way!”
So, if we want to find our own ikigai, where do we start? Start with noticing small pleasures in daily life. That’s the easiest place to begin.
In the brain, there's a chemical called dopamine. When we achieve even small things, dopamine is released, creating happiness. That’s why enjoying small things is so important.
For some, ikigai might seem hard to grasp—especially if life is difficult, if they feel hopeless or lack self-worth. So begin with tiny moments of joy.
Is it the same as positive thinking? Ikigai is a part of that. But when we talk about “positive thinking,” it can feel like pressure to some people. So instead, just notice small joys: making your morning coffee, running in the rain.
Lessons from Ken Mogi:
-
Ikigai is not about chasing success or wealth, but about feeling happiness in your own life, which gives your life personal meaning.
-
Ikigai is not defined by society. Everyone’s ikigai is different. Each person can be happy in their own way.
-
**Don’t judge or force others—**children, partners—to live how you think is right. Respect diversity.
-
Smile at people who are enjoying their ikigai, and support them if they struggle.
-
Ikigai exists on two levels:
-
Big ikigai: life purpose or work values.
-
Small ikigai: tiny joys in everyday life.
-
Ikigai starts with noticing small pleasures today.
Source: From the Cloud of Thoughts column An interview by Ajarn Katewadi from Marumura with Ken Mogi, author of the first Japanese book on ikigai.
-
-
 @ 7e538978:a5987ab6
2025-05-20 14:10:38
@ 7e538978:a5987ab6
2025-05-20 14:10:38🧑💻🚀 This bounty has now been claimed - Read more here 🧑💻🚀🧑💻🚀
Bounty Specification: Implement a Nostr Wallet Connect Funding Source for LNbits
Project Overview
This project involves the development of a funding source within LNbits that can use a remote NWC wallet service.
Objective
To create a NWC funding source for LNbits that allows for lightning network operations using a remote Nostr Wallet Connect wallet service. This funding source should implement all funding source functions using NWC as defined in the Void funding source stub - https://github.com/lnbits/lnbits/blob/dev/lnbits/wallets/void.py
Deliverables
- NWC Funding Source: Robust funding source for LNbits that implements all funding source functions using NIP-47.
- Documentation: Comprehensive guide including:
- Installation and configuration processes.
- Configuration guidelines to connect with various NWC wallet services.
- Test Suite: Complete set of tests ensuring the functionality works under various scenarios and adheres to the NIP-47 protocol.
- Demonstration: A working demonstration of LNbits acting as a NWC client, performing transactions using a NWC wallet service.
Requirements
- The extension should be implemented in Python to align with the existing LNbits platform.
- Follow the NIP-47 protocol.
- Integration should support asynchronous operations to handle real-time transaction confirmations.
Budget
- Total Bounty: 750,000 sats
- Payment will be made upon final delivery, after successful testing and documentation review.
Evaluation Criteria
- Adherence to the NIP-47 specifications and LNbits integration requirements.
- Security and efficiency of the implementation.
- Quality of documentation and ease of use.
How to Apply
Get in touch with us in the LNbits Telegram channel
-
 @ 7e538978:a5987ab6
2025-05-20 14:10:14
@ 7e538978:a5987ab6
2025-05-20 14:10:14🧑💻🚀 This bounty has now been claimed - Read more here 🧑💻🚀
Bounty Specification: Build a Nostr Wallet Connect Wallet Service Extension for LNbits
Project Overview
This project aims to build a Nostr Wallet Connect (NWC) extension for LNbits to allow LNbits to act as a NWC Wallet Service as defined in NIP-47 https://github.com/nostr-protocol/nips/blob/master/47.md
LNbits has an example extension that can be used as a starting point on your extension development journey. Watch the extension build tutorial video here
Objective
To develop a fully functional NWC Wallet Service extension that adheres to the NIP-47 protocol specifications, enabling the following capabilities:
- Generation and handling of Nostr Wallet Connect URIs.
- Processing of payment requests including
pay_invoice,make_invoice,lookup_invoice,list_transactions,get_balance,multi_pay_invoice,pay_keysend,multi_pay_keysendandget_info - Creation and lookup of invoices.
- List and balance querying functionalities.
- Secure communication through encrypted events as per NIP04.
- Implementation of error codes
- Implementation of connection rules with control of the following:
Maximum payment amount,maximum daily budget,connection expiry date(never expire should be an option) denominated in sats.
Deliverables
- NWC Wallet Service Extension Code: Clean, commented, and secure codebase that uses the existing LNbits
nostrclient.pyfunctionality and an LNbits funding source to provide a NWC Wallet Service. - NWC Wallet Service Extension UI: A user interface within the extension that allows a user to connect a new app to the NWC wallet service and edit existing connections. The app connection should allow control of the following rules:
Maximum payment amountMaximum daily budgetConnection expiry date(never expire should be an option) - Documentation: Documentation covering:
- Setup and configuration instructions.
- Usage examples.
- Test Suite: A comprehensive test suite covering all key functionality
Technology Requirements
- The extension must be developed in Python, consistent with the LNbits platform.
- Use of existing LNbits libraries and adherence to its architectural style is required.
- NIP-47 specification must be adhered to.
Budget
- Total Bounty: 750,000 sats
- Payment will be made upon final delivery, after successful testing and documentation review.
Evaluation Criteria
- Adherence to the NIP-47 specifications and LNbits integration requirements.
- Security and efficiency of the implementation.
- Quality of documentation and ease of use.
How to Apply
Get in touch with us in the LNbits Telegram channel
-
 @ bd32f268:22b33966
2025-05-20 14:07:47
@ bd32f268:22b33966
2025-05-20 14:07:47Recentemente tive conhecimento do mais recente flagelo cuja popularidade espelha bem o estado avançado de degeneração da nossa sociedade, o bebé reborn. Há uns anos certamente não passaria de uma piada de mau gosto quando alguém nos dissesse que decidiu adquirir um boneco para criar como se se tratasse de um filho, infelizmente em 2025 deixou de ser uma piada para se tornar algo assombroso.
Depois de fazer alguma pesquisa sobre o tema percebi que há pessoas que têm em curso processos litigantes judiciais relativos à, note-se com pasmo, guarda da boneca. A insanidade não fica por aqui uma vez que, algumas "mães" procuram atendimento médico para os seus bonecos. No Brasil, a câmara dos deputados recebeu três projetos destinados à criação de políticas públicas relacionadas com estes bonecos. As notícias sobre este fenómeno surreal multiplicam-se à medida que a insanidade se alastra como vírus pelas redes sociais.
Vivemos numa sociedade que há muito se divorciou da realidade, uma sociedade de pós-verdade, por isso de alguma forma não choca que este tipo de coisa possa acontecer. Podemos dizer que de alguma forma existe um primado do sentimento face à razão, preferimos, por vezes com consequências catastróficas, uma mentira "empática" do que uma verdade salvífica. Esta nossa tibieza em afirmar a verdade leva-nos consequentemente a uma crendice insustentável que é esta de, cada um tem a sua verdade. Graças a essa filosofia permitimos que um certo discurso lunático tenha mais alcance no espaço público. Por vezes ingenuamente podemos pensar que se trata de algo inofensivo, sem consequências de maior, contudo a experiência mostra-nos precisamente o contrário. Há por detrás destes fenómenos uma índole corrosiva que funciona como aguilhão para a disseminação das agendas políticas e ideológicas que visam a destruição da família. Considerando a excecional vulnerabilidade psíquica que observamos em cada vez mais pessoas neste tempo e a ampla disseminação destes fenómenos temos razão mais que suficientes para estarmos preocupados.
Uma outra elação que podemos retirar é que a nossa sociedade com as alegadas gerações "mais bem preparadas de sempre" está claramente a produzir um excesso de adultos que se comporta e, a todos os títulos são, crianças funcionais.
Com tudo isto fica cada vez mais difícil viver uma vida harmoniosa com a lei natural, pois vivemos em harmonia com algo considerado opressor pelos apologetas destes produtos do marxismo cultural. Com a pretensa igualdade que se pretende alcançar, equiparando inclusive um boneco a uma bebé, as famílias no sentido próprio do termo ficam em segundo plano relativamente a estes "novos" e esotéricos conceitos de família.
Importa perguntar, no meio de todas essas novas formas de se pensar uma família, qual é o ideal ?
Provavelmente os apologetas destas bizarrices ficarão em silêncio uma vez que coerentemente consideram que todas as formas são iguais e válidas.
Isto é apenas mais um sinal que nos é dado do declínio palpável dos valores que construíram a nossa sociedade e civilização. Façamos algo para que estas nocivas ideologias não entrem no nosso coração e em nossas casas, sob pena da corrupção dos nossos princípios e dos daqueles que nos são queridos. Estes fenómenos são de tal forma doentios que nos levam a crer que vivemos numa época tragicómica, o que me fez lembrar de uma história contada por Kierkgaard e que partilho de seguida.
“Certa vez, houve um incêndio num circo ambulante na Dinamarca. O director mandou imediatamente o palhaço, que já se encontrava vestido e maquilhado a preceito, para a vila mais próxima, à procura de ajuda, advertindo-o de que existia o perigo de o fogo se espalhar pelos campos ceifados e ressequidos, com risco iminente para as casas do próprio povoado. O palhaço correu até à vila e pediu aos moradores que viessem ajudar a apagar o incêndio que estava a destruir o circo. Mas os habitantes viram nos gritos do palhaço apenas um belo truque de publicidade que visaria levá-los a acorrer em grande número às sessões do circo; aplaudiam e desatavam a rir. Diante dessa reacção, o palhaço sentiu mais vontade de chorar do que de rir. Fez de tudo para convencer as pessoas de que não estava a representar, de que não se tratava de um truque e sim de um apelo da maior seriedade: estava realmente em causa um incêndio. Mas a sua insistência só fazia aumentar os risos; eles achavam que a performance estava excelente – até que o fogo alcançou de facto aquela vila. Aí já foi tarde, e o fogo acabou por destruir não só o circo, mas também a povoação”.
Soren Kierkgaard - Filósofo dinamarquês
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ cae03c48:2a7d6671
2025-05-20 14:00:00
@ cae03c48:2a7d6671
2025-05-20 14:00:00Bitcoin Magazine

Auradine Expands Bitcoin Mining Solutions with Advanced ASIC Chips, Cooling Systems, and Modular Megawatt ContainersAuradine Inc., a U.S.-based Bitcoin miner manufacturer, today announced it is unveiling a broadened portfolio of mining products at the Bitcoin 2025 Conference in Las Vegas, featuring high-performance ASIC chips, specialized cooling systems, and fully integrated modular containers engineered for scalable, megawatt-class mining operations, according to a press release sent to Bitcoin Magazine.
“Our goal is to democratize access to Bitcoin mining and enable innovative integrations,” said the CEO and Co-Founder of Auradine Rajiv Khemani. “Whether you’re running a megawatt container or building a small form-factor heater-miner for your home, we provide the chips, systems, and support to help you succeed. This new chapter is about giving miners the tools to innovate, scale, and operate efficiently.”
The new ASIC offerings, designed for both industrial and small-scale deployments, support customizable form factors and have already been adopted by operators including MARA Holdings, FutureBit, and Deep South Operating. Alongside the chips, Auradine continues to produce a full range of mining rigs to support a variety of deployment needs.
“Auradine’s ability to deliver both high-performance chips and scalable infrastructure aligns with MARA’s mission to stay at the forefront of bitcoin mining,” stated the Chief Technology Officer of MARA Holdings Ashu Swami. “We have been pleased with the partnership with Auradine with their leading edge engineering capability and innovation.”
Auradine’s modular 1 MW container units, developed in collaboration with Fog Hashing and FBox, are designed to accommodate 100–200 miners each. Merkle Standard, the first to deploy the system, reported improved energy efficiency and operational flexibility.
“We were the first to deploy Auradine’s container solution, and it immediately exceeded our expectations,” said the COO at Merkle Standard Monty Stahl. “The combination of performance, energy efficiency, and modular design gives us the flexibility to scale our operations faster and smarter than traditional infrastructure allows. This is the kind of innovation the mining industry has needed for a long time.”
Their recent $153 million Series C funding supports its push to offer flexible mining infrastructure and supplying ASIC chips for third-party integration. The company also plans to extend its hardware expertise to AI and networking through its AuraLinks initiative.
“We were one of the first to try Auradine’s ASIC chips and were immediately impressed by the support and customization that the team provided,” added the CEO of Deep South Operating, LLC Brock Tompkins. “It helps miners like us to stay scalable and efficient while raising the standard for what decentralized mining looks like.”
This post Auradine Expands Bitcoin Mining Solutions with Advanced ASIC Chips, Cooling Systems, and Modular Megawatt Containers first appeared on Bitcoin Magazine and is written by Oscar Zarraga Perez.
-
 @ 6ad3e2a3:c90b7740
2025-05-20 13:49:50
@ 6ad3e2a3:c90b7740
2025-05-20 13:49:50I’ve written about MSTR twice already, https://www.chrisliss.com/p/mstr and https://www.chrisliss.com/p/mstr-part-2, but I want to focus on legendary short seller James Chanos’ current trade wherein he buys bitcoin (via ETF) and shorts MSTR, in essence to “be like Mike” Saylor who sells MSTR shares at the market and uses them to add bitcoin to the company’s balance sheet. After all, if it’s good enough for Saylor, why shouldn’t everyone be doing it — shorting a company whose stock price is more than 2x its bitcoin holdings and using the proceeds to buy the bitcoin itself?
Saylor himself has said selling shares at 2x NAV (net asset value) to buy bitcoin is like selling dollars for two dollars each, and Chanos has apparently decided to get in while the getting (market cap more than 2x net asset value) is good. If the price of bitcoin moons, sending MSTR’s shares up, you are more than hedged in that event, too. At least that’s the theory.
The problem with this bet against MSTR’s mNAV, i.e., you are betting MSTR’s market cap will converge 1:1 toward its NAV in the short and medium term is this trade does not exist in a vacuum. Saylor has described how his ATM’s (at the market) sales of shares are accretive in BTC per share because of this very premium they carry. Yes, we’ll dilute your shares of the company, but because we’re getting you 2x the bitcoin per share, you are getting an ever smaller slice of an ever bigger overall pie, and the pie is growing 2x faster than your slice is reducing. (I https://www.chrisliss.com/p/mstr how this works in my first post.)
But for this accretion to continue, there must be a constant supply of “greater fools” to pony up for the infinitely printable shares which contain only half their value in underlying bitcoin. Yes, those shares will continue to accrete more BTC per share, but only if there are more fools willing to make this trade in the future. So will there be a constant supply of such “fools” to keep fueling MSTR’s mNAV multiple indefinitely?
Yes, there will be in my opinion because you have to look at the trade from the prospective fools’ perspective. Those “fools” are not trading bitcoin for MSTR, they are trading their dollars, selling other equities to raise them maybe, but in the end it’s a dollars for shares trade. They are not selling bitcoin for them.
You might object that those same dollars could buy bitcoin instead, so they are surely trading the opportunity cost of buying bitcoin for them, but if only 5-10 percent of the market (or less) is buying bitcoin itself, the bucket in which which those “fools” reside is the entire non-bitcoin-buying equity market. (And this is not considering the even larger debt market which Saylor has yet to tap in earnest.)
So for those 90-95 percent who do not and are not presently planning to own bitcoin itself, is buying MSTR a fool’s errand, so to speak? Not remotely. If MSTR shares are infinitely printable ATM, they are still less so than the dollar and other fiat currencies. And MSTR shares are backed 2:1 by bitcoin itself, while the fiat currencies are backed by absolutely nothing. So if you hold dollars or euros, trading them for MSTR shares is an errand more sage than foolish.
That’s why this trade (buying BTC and shorting MSTR) is so dangerous. Not only are there many people who won’t buy BTC buying MSTR, there are many funds and other investment entities who are only able to buy MSTR.
Do you want to get BTC at 1:1 with the 5-10 percent or MSTR backed 2:1 with the 90-95 percent. This is a bit like medical tests that have a 95 percent accuracy rate for an asymptomatic disease that only one percent of the population has. If someone tests positive, it’s more likely to be a false one than an indication he has the disease*. The accuracy rate, even at 19:1, is subservient to the size of the respective populations.
At some point this will no longer be the case, but so long as the understanding of bitcoin is not widespread, so long as the dollar is still the unit of account, the “greater fools” buying MSTR are still miles ahead of the greatest fools buying neither, and the stock price and mNAV should only increase.
. . .
One other thought: it’s more work to play defense than offense because the person on offense knows where he’s going, and the defender can only react to him once he moves. Similarly, Saylor by virtue of being the issuer of the shares knows when more will come online while Chanos and other short sellers are borrowing them to sell in reaction to Saylor’s strategy. At any given moment, Saylor can pause anytime, choosing to issue convertible debt or preferred shares with which to buy more bitcoin, and the shorts will not be given advance notice.
If the price runs, and there is no ATM that week because Saylor has stopped on a dime, so to speak, the shorts will be left having to scramble to change directions and buy the shares back to cover. Their momentum might be in the wrong direction, though, and like Allen Iverson breaking ankles with a crossover, Saylor might trigger a massive short squeeze, rocketing the share price ever higher. That’s why he actually welcomes Chanos et al trying this copycat strategy — it becomes the fuel for outsized gains.
For that reason, news that Chanos is shorting MSTR has not shaken my conviction, though there are other more pertinent https://www.chrisliss.com/p/mstr-part-2 with MSTR, of which one should be aware. And as always, do your own due diligence before investing in anything.
* To understand this, consider a population of 100,000, with one percent having a disease. That means 1,000 have it, 99,000 do not. If the test is 95 percent accurate, and everyone is tested, 950 of the 1,000 will test positive (true positives), 50 who have it will test negative (false negatives.) Of the positives, 95 percent of 99,000 (94,050) will test negative (true negatives) and five percent (4,950) will test positive (false positives). That means 4,950 out of 5,900 positives (84%) will be false.
-
 @ 7e538978:a5987ab6
2025-05-20 13:45:12
@ 7e538978:a5987ab6
2025-05-20 13:45:12LNbits now has full NWC support thanks to the work of contributor @riccardobl, who has claimed two LNbits bounties for implementing Nostr Wallet Connect (NWC) support in LNbits.
LNbits can now act both as a wallet service and as a funding source using the Nostr NWC protocol (NIP-47). This opens the door to new integrations with a growing ecosystem of Nostr clients and Lightning wallets.
Two Sides of NWC Integration
The work delivered by Riccardo B comprises two separate peices of work that together implement full support for NWC:
1. LNbits as a Wallet Service
This extension allows LNbits to operate as an always-on wallet service compatible with Nostr Wallet Connect clients such as Damus, Amethyst, or any app supporting NIP-47. Users can connect these Nostr clients to their LNbits instance and create and pay Lightning invoices through it.
This turns your LNbits wallet into a backend Lightning provider for your favourite Nostr app all self-hosted.
2. NWC as a Funding Source
The second piece of work flips the relationship. With this in place, LNbits can now act as an NWC client, meaning it can be funded from any NWC wallet service. This could be another LNbits, Alby, Minibits and more.
Why This Is a Big Deal for LNbits Users
These two bounties make LNbits one of the first applications in the Lightning ecosystem to offer bidirectional NWC support — as both a service and a client. This brings benefits such as:
-
Fund any NWC-compatible app using your LNbits wallet.
-
Fund LNbits using any wallet that supports Nostr Wallet Connect.
-
Build NWC-native apps with LNbits as a backend, or power your own LNbits server using existing wallet infrastructure.
For developers, it’s a chance to build in flexible, interoperable ways. For users, it means more choice, more control, and less friction when managing Lightning payments across apps and devices.
Both of these features were developed and delivered by Riccardo B (@riccardobl), an contributor who took on and completed both LNbits bounties and was extremely helpful during the PR review process. We owe a huge thanks to Riccardo for his work here.
To try them out, read the full article detailing how NWC works with LNbits.
-
-
 @ c6d8334c:30883d6d
2025-05-20 14:08:19
@ c6d8334c:30883d6d
2025-05-20 14:08:19🔑 Hashtag-Kombination (immer gleich aufgebaut):
```
relilab #verstehen 1️⃣
relilab #anwenden 2️⃣
relilab #reflektieren
relilab #gestalten 3️⃣
```
✅ Pflicht:
-
#relilab -
genau ein Kompetenz-Hashtag:
#verstehen,#anwenden,#reflektieren,#gestalten
✨ Optional:
-
eine Niveaustufe:
-
1️⃣ Reproduktion
-
2️⃣ Rekonstruktion
-
3️⃣ Konstruktion
📝 Beispielhafte Posts
```text
relilab #verstehen 1️⃣
Ich habe heute zum ersten Mal ausprobiert, wie KI überhaupt "lernt". Spannend!
relilab #anwenden 2️⃣
ChatGPT half mir dabei, einen Ablaufplan für einen Unterricht zu entwerfen – sehr hilfreich.
relilab #reflektieren
Welche Rolle spielt das Menschenbild, wenn KI religiöse Themen behandelt?
relilab #gestalten 3️⃣
Ich habe ein eigenes H5P-Modul mit einem KI-generierten Bibelquiz gebaut. Wer testet es? ```
-
-
 @ 662f9bff:8960f6b2
2025-05-20 13:44:39
@ 662f9bff:8960f6b2
2025-05-20 13:44:39Currently, and for the last three weeks, I am in Belfast. With the situation in HK becoming ever more crazy by the day we took the opportunity to escape from Hong Kong for a bit - I escaped with V and 3 suitcases. I also have some family matters that I am giving priority to at this time. We plan to stay a few more weeks in Northern Ireland and then after some time in Belgium we will be visiting some other European locations. I do hope that HK will be a place that we can go back to - we will see...
What's happening?
Quite a few significant events have happened in the last few weeks that deserve some deeper analysis and checking than you will ever get from the media propaganda circus that is running full force at the moment. You should be in no doubt that the "Great Reset" with its supporting "Great Narrative" is in full swing.
In most of the world the C19 story has run its course - for now. Most countries seem to have have "declared victory" and "moved on". Obviously HK is an exception (nothing happened there for the last two years) and I fear they will get to experience the whole 2-year thing in the coming 3-4 months. Watch out - the politicians everywhere are looking to permanently establish the "emergency controls" as "normal" - see previous Letter for some examples in Ireland and EU.
Invasion of Ukraine has led to so many lines being crossed - to the extent that clearly things will never be the same again in our lifetime.
Why? How did we get here?
I do not claim to know all the answers but some things are fairly clear if you look with open eyes and the wisdom that previous generations and civilisations have made available to us - even if most choose to ignore it (Plato on the flaws of democracy). Those who do not learn from history are doomed to repeat it and even those who learn will have litle choice but to go along for much of the ride.
Perhaps my notes and the links below will help you to form an educated opinion rather than the pervasive propaganda we are all being fed.
The current situation is more than 100 years in the making and much (if not most) of what you thought was true is less veracious than you could ever imagine. No doubt we could (and maybe should) go back further but let's start in 1913 when the British Government asked the public no longer to request exchange of their pounds for gold coins at the post office. This led to the issuing of War Bonds and fractional reserve accounting that allowed the Bank of England essentially to print unlimited money to fight in WW1; without this devious action they would have been constrained to act within the limits of the country's reserves and WW1 would have been shorter. Read The Fiat Standard for more details on how this happened. Around this time, and likely no coincidence, the US bankers were scheming how to get around the constitutional controls against such actions in their own country - read more in The Creature from Jekyll Island.
Following WW1, Germany was forced to pay war reparations in Gold (hard money). This led to a decade of money printing and extravagant excesses and crashes as hyperinflation set in, ending in the bankrupting of the country and the nationalism that fed WW2 - the gory details of devaluation and hyperinflation in Weimar Germany are described in When Money Dies. Meanwhile the US bankers who had been preparing since 1913 stepped in with unlimited money printing to fund WW2 and then also in their Marshal Plan to cement in place the Bretton Woods post-war agreement that made US Dollar the global reserve currency.
Decades of boom and bust followed - well explained by Ray Dalio who portrays this as perfectly normal and to be expected - unfortunately it is for soft (non-hard) money based economies. The Fourth Turning will give many additional insights to this period too as well as cycles to watch for and their cause and nature. In 1961 Eisenhower tried to warn the population in his farewell address about the "Military Industrial Complex" and many believe that Robert Kennedy's assassination in 1963 may well be not entirely unrelated.
Things came to a head in August 1971 when the countries of the world realised that the US was (contrary to all promises) printing unlimited funds to (among other things) fight the Vietnam war and so undermining the expected and required convertibility of US dollars (the currency of global trade) for Gold (hard money). A French warship heading to NY to collect France's gold was the straw that caused Nixon to default on US Debt convertibility and "close the gold window".
This in turn led to further decades of increasing financialization, further fuelled (pun intended) by the PetroDollar creation and "exorbitant priviledge" that the US obtained by having the global reserve currency - benefiting those closest to the money supply (Cantillon effect) while hollowing out the US manufacturing and eventually devastating its middle and working classes (Triffin dilemma) - Arthur Hayes describes all this and much more as well as the likely outlook in his article - Energy Canceled. Absolutely required reading or listen to Guy Swan reading it and giving his additional interpetation.
Zoltan Pozsar of Credit Suisse explains how the money system is now being reset following the events of last few weeks and his article outlines a likely way forward - Bretton Woods III. His paper is somewhat dense, heavy reading and you might prefer to listen to Luc Gromen's more conversational explainer with Marty
All of this was well known to our forefathers
The writers of the American Constitution understood the dangers of money being controlled by any elite group and they did their best to include protections in the US constitution. It did take the bankers multiple decades and puppet presidents to circumvent these but do so they did. Thomas Jefferson could not have been more clear in his warning.
" If the American people ever allow private banks to control the issue of their currency, first by inflation, then by deflation, the banks and corporations that will grow up around(these banks) will deprive the people of all property until their children wake up homeless on the continent their fathers conquered."
Islamic finace also recognised the dangers - you will likely be aware of the restrictions that forbid interest payments - read this interesting article from The Guardian
You will likely also be aware from schooldays that the Roman Empire collapsed because it expanded too much and the overhead became unbearable leading to the debasement of its money and inability to extract tax payments to support itself. Read more from Mises Institute. Here too, much of this will likely ring familiar.
So what can you do about it?
In theory Governments should respect Consent of the Governed and the 1948 Universal Declaration of Human Rights states that "The will of the people shall be the basis of the authority of government".
For you to decide if and to what extent governments today are acting in line with these principles. If not, what can you do about it?
The options you have are basically - Loyalty, Voice or Exit. 1. You can be loyal and accept what you are told - 2. you may (or may not) be able to voice disagreement and 3. you may (or may not!) be able to exit. Authoritarian governments will make everything except Loyalty difficult or even impossible - if in doubt, read George Orwell 1984 - or look just around at recent events today in many countries.
I'll be happy to delve deeper into this in subsequent letters if there is interest - for now I recommend you to read Sovereign Individual. It is a long read but each chapter starts with a summary and you can read the summaries of each chapter as a first step. Also - I'm happy to discuss with you - just reach out and let me know!
For those who prefer a structured reading list, check References
That's it!
No one can be told what The Matrix is.\ You have to see it for yourself.**
Do share this newsletter with any of your friends and family who might be interested.
You can easily ask questions or discuss any topics in the newsletters in our Telegram group - click the link here to join the group.\ You can also email me at: LetterFrom@rogerprice.me
💡Enjoy the newsletters in your own language : Dutch, French, German, Serbian, Chinese Traditional & Simplified, Thai and Burmese.
-
 @ 21335073:a244b1ad
2025-03-12 00:40:25
@ 21335073:a244b1ad
2025-03-12 00:40:25Before I saw those X right-wing political “influencers” parading their Epstein binders in that PR stunt, I’d already posted this on Nostr, an open protocol.
“Today, the world’s attention will likely fixate on Epstein, governmental failures in addressing horrific abuse cases, and the influential figures who perpetrate such acts—yet few will center the victims and survivors in the conversation. The survivors of Epstein went to law enforcement and very little happened. The survivors tried to speak to the corporate press and the corporate press knowingly covered for him. In situations like these social media can serve as one of the only ways for a survivor’s voice to be heard.
It’s becoming increasingly evident that the line between centralized corporate social media and the state is razor-thin, if it exists at all. Time and again, the state shields powerful abusers when it’s politically expedient to do so. In this climate, a survivor attempting to expose someone like Epstein on a corporate tech platform faces an uphill battle—there’s no assurance their voice would even break through. Their story wouldn’t truly belong to them; it’d be at the mercy of the platform, subject to deletion at a whim. Nostr, though, offers a lifeline—a censorship-resistant space where survivors can share their truths, no matter how untouchable the abuser might seem. A survivor could remain anonymous here if they took enough steps.
Nostr holds real promise for amplifying survivor voices. And if you’re here daily, tossing out memes, take heart: you’re helping build a foundation for those who desperately need to be heard.“
That post is untouchable—no CEO, company, employee, or government can delete it. Even if I wanted to, I couldn’t take it down myself. The post will outlive me on the protocol.
The cozy alliance between the state and corporate social media hit me hard during that right-wing X “influencer” PR stunt. Elon owns X. Elon’s a special government employee. X pays those influencers to post. We don’t know who else pays them to post. Those influencers are spurred on by both the government and X to manage the Epstein case narrative. It wasn’t survivors standing there, grinning for photos—it was paid influencers, gatekeepers orchestrating yet another chance to re-exploit the already exploited.
The bond between the state and corporate social media is tight. If the other Epsteins out there are ever to be unmasked, I wouldn’t bet on a survivor’s story staying safe with a corporate tech platform, the government, any social media influencer, or mainstream journalist. Right now, only a protocol can hand survivors the power to truly own their narrative.
I don’t have anything against Elon—I’ve actually been a big supporter. I’m just stating it as I see it. X isn’t censorship resistant and they have an algorithm that they choose not the user. Corporate tech platforms like X can be a better fit for some survivors. X has safety tools and content moderation, making it a solid option for certain individuals. Grok can be a big help for survivors looking for resources or support! As a survivor, you know what works best for you, and safety should always come first—keep that front and center.
That said, a protocol is a game-changer for cases where the powerful are likely to censor. During China's # MeToo movement, survivors faced heavy censorship on social media platforms like Weibo and WeChat, where posts about sexual harassment were quickly removed, and hashtags like # MeToo or "woyeshi" were blocked by government and platform filters. To bypass this, activists turned to blockchain technology encoding their stories—like Yue Xin’s open letter about a Peking University case—into transaction metadata. This made the information tamper-proof and publicly accessible, resisting censorship since blockchain data can’t be easily altered or deleted.
I posted this on X 2/28/25. I wanted to try my first long post on a nostr client. The Epstein cover up is ongoing so it’s still relevant, unfortunately.
If you are a survivor or loved one who is reading this and needs support please reach out to: National Sexual Assault Hotline 24/7 https://rainn.org/
Hours: Available 24 hours
-
 @ 04c915da:3dfbecc9
2025-03-10 23:31:30
@ 04c915da:3dfbecc9
2025-03-10 23:31:30Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Usually stolen bitcoin for the reserve creates a perverse incentive. If governments see a bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 6ad3e2a3:c90b7740
2025-05-20 13:44:28
@ 6ad3e2a3:c90b7740
2025-05-20 13:44:28I https://www.chrisliss.com/p/mstr a few months ago with the subtitle “The Only Stock,” and I’m starting to regret it. Now, it was trading at 396 on January 20 when I posted it and 404 now (even if it dipped 40 percent to 230 or so in between), but that’s not why I regret it. I pointed out it was not investable unless you’re willing to stomach large drawdowns, and anyone who bought then could exit with a small profit now had they not panic-sold along the way.
The reason I regret it is I don’t want to make public stock predictions because it adds stress to my life. I have not sold any of my shares yet, but something I’ve noticed recently has got me thinking about it, and stock tips are like a game of telephone wherein whoever is last in the chain might find out the wrong information and too late. And while every adult has agency and is responsible for his own financial decisions, I don’t want my readers losing money on account of anything I write.
My base case is still that MSTR becomes a trillion-dollar company, destroys the performance of the S&P, the Mag-7 and virtually any other equity portfolio most people would assemble. Michael Saylor is trading an infinitely-printable asset (his shares) for humanity’s best-ever, finite-supply digital gold, and that trade should be profitable for him and his shareholders in perpetuity.
I don’t know exactly what he plans to do when that trade is no longer available to him — either because no one takes fiat currency for bitcoin anymore or because his mNAV (market-cap-to-bitcoin-holding ratio) goes below one — but that’s not my main concern, either. At that point he’ll have so much bitcoin, he’ll probably become the world’s first and largest bitcoin bank and profit by making his pristine collateral available to individuals and institutions. Even at five percent interest, half a trillion in bitcoin would yield $25B in profits every year. Even at a modest 10x valuation, the stock would more than double from here.
I am also not overly concerned with Saylor’s present amount of convertible debt which is at low or zero rates and is only https://www.strategy.com/. He’s been conservative on that front and only issuing on favorable terms. I don’t doubt Saylor’s prescience, intelligence or business sense one bit.
What got me thinking were some Twitter posts by a former Salomon Brothers trader/prophet Josh Mandell https://x.com/JoshMandell6/status/1921597739458339193 recently. In November when bitcoin was mooning after the election, he predicted that on March 14th it would close at $84,000, and if it did it would then go on an epic run up to $444,000 this cycle.
A lot of people make predictions, a few of them come true, but rarely do they come true on the dot (it closed at exactly $84K according to some exchanges) and on such a specific timeframe. Now, maybe he just got lucky, or maybe he is a skilled trader who made one good prediction, but the reason he gave for his prediction, insofar as he gave one, was not some technical chart or quantitative analysis, but a memory he had from 30 years ago that got into his mind that he couldn’t shake. He didn’t get much more specific than that, other than that he was tuned into something that if he explained fully would make too many people think he had gone insane. And then the prediction came true on the dot months later.
Now I believe in the paranormal more than the average person. I do not think things are random, and insofar as they appear that way it’s only because we have incomplete information — even a coin toss is predictable if you knew the exact force and spin that was put on the coin. I think for whatever reason, this guy is plugged into something, and while I would never invest a substantial amount of money on that belief — not only are earnestly-made prophecies often delusions or even if correct wrongly interpreted — that he sold makes me think.
He gave more substantive reasons for selling than prophecy, by the way — he seems to think Saylor’s perpetual issuance of shares ATM (at the market) to buy more bitcoin is putting too much downward pressure on the stock. Obviously, selling shares — even if to buy the world’s most pristine collateral at a 2x-plus mNAV — reduces the short-term appreciation of those shares.
His thesis seems to be that Saylor is doing this even if he would be better off letting the price appreciate more, attracting more investors, squeezing more shorts, etc because he needs to improve his credit rating to tap into the convertible debt market to the extent he has promised ($42 billion more over the next few years) at favorable terms. But in doing this, he is souring common stock investors because they are not seeing the near-term appreciation they should on their holdings.
Now this is a trivial concern if over the long haul MSTR does what it has the last couple years which is to outperform by a wide margin not only every large cap stock and the S&P but bitcoin itself. And the bigger his stack of bitcoin, the more his stock should appreciate as bitcoin goes up. But markets do not operate linearly and rationally. Should he sour prospective buyers to a great enough extent, should he attract shorts (and supply them with available shares to borrow) to a great enough extent, perhaps there might be an mNAV-crushing cascade that drives people into other bitcoin treasury companies, ETFs or bitcoin itself.
Now Saylor as first mover and by far the largest publicly-traded treasury company has a significant advantage. Institutions are far less likely to invest in size in smaller treasury companies with shorter track records, and many of them are not allowed to invest in ETFs or bitcoin at all. And even if a lot of money did go into any of those vehicles, it would only drive the value of his assets up and hence his stock price, no matter the mNAV. But Josh Mandell sold his shares prior to a weekend where bitcoin went from 102K to 104K, the US announced a deal with China, the mag-7 had a big spike (AAPL was up 6.3 percent) and then MSTR’s stock went down from 416 to 404. As I said, he is on to something.
So what’s the real long-term risk? I don’t know. Maybe there’s something about the nature of bitcoin that long-term is not really amenable to third-party custody and administration. It’s a bearer asset (“not your keys, not your coins”), and introducing counterparty risk is antithetical to its core purpose, the separation of money and state, or in this case money and bank.
With the bitcoin network you can literally “be your own bank.” To transact in digital dollars you need a bank account — or at least a stable coin one mediated by a centralized entity like Tether. You can’t hold digital dollars in your mind via some memorized seed words like you can bitcoin, accessible anywhere in the world, the ledger of which is maintained by tens of thousands of individually-run nodes. This property which democratizes value storage in the way gold did, except now you can wield your purchasing power globally, might be so antithetical to communal storage via corporation or bank that doing so is doomed to catastrophe.
We’ve already seen this happen with exchanges via FTX and Mt. Gox. Counterparty risk is one of the problems bitcoin was created to solve, so moving that risk from a fractionally reserved international banking system to corporate balance sheets still very much a part of that system is probably not the seismic advancement integral to the technology’s promise.
But this is more of a philosophical concern rather than a concrete one. To get more specific, it’s easy to imagine Coinbase, if indeed that’s where MSTR custodies its coins, gets hacked or https://www.chrisliss.com/p/soft-landing, i.e., seized by an increasingly desperate and insolvent government. Or maybe Coinbase simply doesn’t have the coins it purports like FTX, or a rogue band of employees, working on behalf of some powerful faction for “https://www.chrisliss.com/national-security-and-public-healt” executes the rug pull. Even if you deem these scenarios unlikely, they are not unfathomable.
Beyond outright counterparty malfeasance, there are other risks — what if owning common stock in an enterprise that simply holds bitcoin falls out of favor? Imagine if some new individual custody solution emerges wherein you have direct access to the coins themselves in an “even a boomer can do this” kind of way wherein there’s no compelling reason to own common stock with its junior claims to the capital stack in the event of insolvency? Why stand in line behind debt holders and preferred shares when you can invest in something that’s directly withdrawable and accessible if world events spike volatility to a systemic breaking point?
Things need not even get that rocky for this to be a concern — just the perception that they might could spook people into realizing common stock of a corporate balance sheet might be less than ideal as your custody solution.
Moreover, Saylor himself presents some risk. He could be compromised or blackmailed, he could lose his cool or get into an accident. These are low-probability scenarios, but also not unfathomable as any single point of failure is a target, especially for those factions who stand to lose unimaginable wealth and power should his speculative attack on the system succeed at scale.
Finally, even if Saylor remains free to operate as he sees fit, there is what I’d call the Icarus risk — he might be too ambitious, too hell-bent on acquiring bitcoin at all costs, too much of a maniac in service of his vision. Remember, he initially bought bitcoin during the covid crash and concomitant massive money print upon his prescient realization that businesses providing goods and services couldn’t possibly keep pace with inflation over the long haul. He was merely playing defense to preserve his capital, and now, despite his sizable lead and secured position is still throwing forward passes in the fourth quarter rather than running out the clock and securing the W.
Saylor is now arguably less a bitcoin maximalist and advocate, articulately making the case for superior money and individual sovereignty, but a corporate titan hell-bent on world domination via apex-predator-status balance sheet. When is enough enough? Many of the greatest conquerors in history pushed their empires too far until they fractured. In fact, 25 years ago MSTR was a big winner before the dot-com crash during which its stock price and most of Saylor’s fortune were wiped out when he was sued by the SEC for accounting fraud (he subsequently settled).
Now it’s possible, he learned from that experience, got up off the mat and figured out how to avoid his youthful mistakes. But it’s also possible his character is such that he will repeat it again, only this time at scale.
But as I said, my base case is MSTR is a trillion-dollar market cap, and the stock runs in parallel with bitcoin’s ascendance over the next decade. Saylor has been https://www.strategy.com/, prescient, bold and responsible so far over this iteration. I view Mandell’s concerns as valid, but similar to Wall St’s ones about AMZN’s Jeff Bezos who relentlessly ignored their insistence on profitability for a decade as he plowed every dollar into building out productive capacity and turned the company into the $2T world-dominating retail giant it is now.
Again, I haven’t (yet) sold any of my shares or even call options. But because I posted about this in January I felt I should at least follow-up with a more detailed rundown of what I take to be the risks. As always, do your own due diligence with any prospective investment.
-
 @ 6ad3e2a3:c90b7740
2025-05-20 13:38:04
@ 6ad3e2a3:c90b7740
2025-05-20 13:38:04When I was a kid, I wanted to be rich, but found the prospect of hard work tedious, pointless and soul-crushing. Instead of studying for exams, getting some job and clawing your way up the ladder, I wondered why we couldn’t just build a device that measured your brain capacity and awarded you the money you would have made had you applied yourself. Eliminate the middleman, so to speak, the useless paper pushing evoked by the word “career.”
But when you think about it, it’s not really money you’re after, as money is but purchasing power, and so it’s the things money can provide like a nice lifestyle and the peace of mind that comes from not worrying about it. And it’s not really the lifestyle or financial independence, per se, since moment to moment what’s in your bank account isn’t determining your mental state, but the feeling those things give you — a sense of expansiveness and freedom.
But if you did have such a machine, and it awarded you the money, you probably wouldn’t have that kind of expansiveness and freedom, especially if you did nothing to achieve those things. You would still feel bored, distracted and unsatisfied despite unrestricted means to travel or dine out as you saw fit. People who win the lottery, for example, tend to revert to their prior level of satisfaction in short order.
The feeling you really want then is the sense of rising to a challenge, negotiating and adapting to your environment, persevering in a state of uncertainty, tapping into your resourcefulness and creativity. It’s only while operating at the edge of your capacity you could ever be so fulfilled. In fact, in such a state the question of your satisfaction level would never come up. You wouldn’t even think to wonder about it you’d be so engrossed.
So what you really crave is a mind device that encourages you to adapt to your environment using your full creative capabilities in the present moment, so much so you realize if you do not do this, you have the sense of squandering your life in a tedious, pointless and soul-crushing way. You need to be totally stuck, without the option of turning back. In sum, you need to face reality exactly as it is, without any escape therefrom.
The measure of your mind in that case is your reality itself. The device is already with you — it’s the world you are presently creating with the consciousness you have, providing you avenues to escape, none of which are satisfactory, none that can lead to the state you truly desire. You have a choice to pursue them fruitlessly and wind up at square one, or to abandon them and attain your freedom. No matter how many times you go down a false road, you wind up at the same place until you give up on the Sisyphean task and proceed in earnest.
My childhood fantasy was real, it turns out, only I had misunderstood its meaning.
-
 @ 732c6a62:42003da2
2025-03-09 22:36:26
@ 732c6a62:42003da2
2025-03-09 22:36:26Não são recentes as táticas da esquerda de tentar reprimir intelectualmente seus opositores na base do deboche, da ironia, do desprezo e do boicote à credibilidade. Até Marx usava ironia para chamar os críticos de "burgueses iludidos". A diferença é que, no século XXI, trocaram o manifesto comunista por threads no Twitter e a dialética por memes de mau gosto.
A Falácia da Superioridade Moral
O debate sobre o "pobre de direita" no Brasil é contaminado por uma premissa tácita da esquerda: a ideia de que classes baixas só podem ter consciência política se aderirem a pautas progressistas. Quem ousa divergir é tratado como "traidor de classe", "manipulado", "ignorante", ou até vítimas de deboches como alguma pessoa com um qi em temperatura ambiente repetir diversas vezes "não é possível que ainda exista pobre de direita", "nunca vou entender pobre de direita", ou "pobre de direita é muito burro, rico eu até entendo", como se o autor dessas frases fosse o paladino dos mais oprimidos e pobres. Esse discurso, porém, não resiste a uma análise empírica, histórica ou sociológica.
Contexto Histórico: A Esquerda e o Mito do "Voto Consciente"
A noção de que o pobre deve votar na esquerda por "interesse de classe" é herança do marxismo ortodoxo, que via a política como mero reflexo da posição econômica. No entanto, a realidade é mais complexa:
- Dados do Latinobarómetro (2022): 41% dos brasileiros de baixa renda (até 2 salários mínimos) apoiam redução de impostos e maior liberdade econômica — pautas tradicionalmente associadas à direita.
- Pesquisa IPEC (2023): 58% dos pobres brasileiros priorizam "segurança pública" como principal demanda, acima de "distribuição de renda".
Esses números não são acidentais. Refletem uma mudança estrutural: o pobre moderno não é mais o "operário industrial" do século XX, mas um empreendedor informal, motorista de app, ou microempresário — figuras que valorizam autonomia e rejeitam paternalismo estatal. Eles dizem não entender o pobre de direita e que nunca vai entendê-los, mas o fato é que não entendem porque nunca conversaram com um sem fazer cara de psicólogo de posto de saúde. Sua "preocupação" é só uma máscara para esconder o desprezo por quem ousa pensar diferente do seu manual de "oprimido ideal".
Se ainda não entenderam:
Direita ≠ rico: Tem gente que trabalha 12h/dia e vota em liberal porque quer ser dono do próprio negócio, não pra pagar mais taxação pra você postar meme no Twitter.
Acham que são o Sherlock Holmes da pobreza: o palpite de que "o pobre é manipulado" é tão raso quanto sua compreensão de economia básica.
A Psicologia por Trás do Voto Conservador nas Periferias
A esquerda atribui o voto pobre em direita a "falta de educação" ou "manipulação midiática". Essa tese é não apenas elitista, mas cientificamente falsa:
Análise Psicológica Básica (para você que se acha o Paulo Freire):
- Síndrome do Branco Salvador: Acha que o pobre é uma criatura tão frágil que precisa de você pra pensar. Spoiler: ele não precisa.
- Viés da Superioridade Moral: "Se você é pobre e não concorda comigo, você é burro". Parabéns, recriou a escravidão intelectual.
- Efeito Dunning-Kruger: Não sabe o que é CLT, mas dá palpite sobre reforma trabalhista.- Estudo da Universidade de São Paulo (USP, 2021): Entre moradores de favelas, 63% associam políticas de segurança dura (como "bandido bom é bandido morto") à proteção de seus negócios e famílias. Para eles, a esquerda é "branda demais" com o crime.
- Pesquisa FGV (2020): 71% dos trabalhadores informais rejeitam aumentos de impostos, mesmo que para financiar programas sociais. Motivo: já sofrem com a burocracia estatal para legalizar seus negócios.
Esses dados revelam uma racionalidade prática: o pobre avalia políticas pelo impacto imediato em sua vida, não por abstrações ideológicas. Enquanto a esquerda fala em "reforma estrutural" e tenta importar discursos estrangeiros para debate, por exemplo, o tema irrelevante do pronome neutro, ele quer resolver problemas como:
- Violência (que afeta seu comércio);
- Impostos (que consomem até 40% do lucro de um camelô);
- Burocracia (que impede a legalização de sua barraca de pastel).
Religião, Valores e a Hipocrisia do "Ateísmo de Redes Sociais"
A esquerda subestima o papel da religião na formação política das classes baixas. No Brasil, 76% dos evangélicos são pobres (Datafolha, 2023), e suas igrejas promovem valores como:
- Família tradicional (contra pautas progressistas como ideologia de gênero em escolas);
- Auto-responsabilidade (ênfase em "trabalho duro" em vez de assistencialismo).Exemplo Concreto:
Nas favelas de São Paulo, pastores evangélicos são frequentemente eleitos a cargos locais com plataformas anticrime e pró-mercado. Para seus eleitores, a esquerda urbana (que defende descriminalização de drogas e críticas à polícia) representa uma ameaça ao seu estilo de vida.
A Esquerda e seu Desprezo pela Autonomia do Pobre
O cerne do debate é a incapacidade da esquerda de aceitar que o pobre possa ser autônomo. Algumas evidências:
O Caso dos Empreendedores Informais
- Segundo o IBGE (2023), 40% dos trabalhadores brasileiros estão na informalidade. Muitos veem o Estado como obstáculo, não aliado. Políticas de direita (como simplificação tributária) são mais atraentes para eles que o Bolsa Família.
A Ascensão do Conservadorismo Periférico
- Pessoas assim tem um pensamento simples. Sua mensagem: "Queremos empreender, não depender de político."
A Rejeição ao "Vitimismo"
- Pesquisa Atlas Intel (2022): 68% dos pobres brasileiros rejeitam o termo "vítima da sociedade". Preferem ser vistos como "lutadores".
A projeção freudiana "o pobre é burro porque eu sou inteligente"
O deboche esquerdista esconde um complexo de inferioridade disfarçado de superioridade moral. É a Síndrome do Salvador em sua forma mais patética:
- Passo 1: Assume-se que o pobre é um ser desprovido de agência.
- Passo 2: Qualquer desvio da narrativa é atribuído a "manipulação da elite".
- Passo 3: Quem critica o processo é chamado de "fascista".Exemplo Prático:
Quando uma empregada doméstica diz que prefere o livre mercado a programas sociais, a esquerda não pergunta "por quê?" — ela grita "lavagem cerebral!". A ironia? Essa mesma esquerda defende a autonomia feminina, exceto quando a mulher é pobre e pensa diferente.Dados Globais: O Fenômeno Não é Brasileiro
A ideia de que "pobre de direita" é uma anomalia é desmentida por evidências internacionais:
- Estados Unidos: 38% dos eleitores com renda abaixo de US$ 30k/ano votaram em Trump em 2020 (Pew Research). Motivos principais: conservadorismo social e rejeição a impostos. A esquerda: "vítimas da falsa consciência". Mais um detalhe: na última eleição de 2024, grande parte da classe "artística" milionária dos Estados Unidos, figuras conhecidas, promoveram em peso a Kamala Harris, do Partido Democrata. Percebe como a esquerda atual é a personificaçãoda burguesia e de só pensar na própria barriga?
- Argentina: Javier Milei, libertário radical, quando candidato, tinha forte apoio nas villas miseria (favelas). Seu lema — "O estado é um parasita" — ressoa entre quem sofria com inflação de 211% ao ano.
- Índia: O partido BJP (direita nacionalista) domina entre os pobres rurais, que associam a esquerda a elites urbanas desconectadas de suas necessidades.
A história que a esquerda tenta apagar: pobres de direita existem desde sempre
A esquerda age como se o "pobre de direita" fosse uma invenção recente do MBL, mas a realidade é que classes baixas conservadoras são regra, não exceção, na história mundial:
- Revolução Francesa (1789): Camponeses apoiaram a monarquia contra os jacobinos urbanos que queriam "libertá-los".
- Brasil Imperial: Escravos libertos que viraram pequenos proprietários rurais rejeitavam o abolicionismo radical — queriam integração, não utopia.Tradução:
Quando o pobre não segue o script, a esquerda inventa teorias conspiratórias.
A Hipocrisia da Esquerda Urbana e Universitária
Enquanto acusa o pobre de direita de "alienado", a esquerda brasileira é dominada por uma elite desconectada da realidade periférica:
- Perfil Socioeconômico: 82% dos filiados ao PSOL têm ensino superior completo (TSE, 2023). Apenas 6% moram em bairros periféricos.
- Prioridades Descoladas: Enquanto o pobre debate segurança e custo de vida, a esquerda pauta discussões como "linguagem não-binária em editais públicos" — tema irrelevante para quem luta contra o desemprego. Os grandes teóricos comunistas se reviram no túmulo quando veem o que a esquerda se tornou: não debatem os reais problemas do Brasil, e sim sobre suas próprias emoções.
"A esquerda brasileira trocou o operário pelo influencer progressista. O pobre virou um personagem de campanha, não um interlocutor real."
A diversidade de pensamento que a esquerda não suporta
A esquerda prega diversidade — desde que você seja diverso dentro de um checklist pré-aprovado. Pobre LGBTQ+? Herói. Pobre evangélico? Fascista. Pobre que abre MEI? "Peão do capitalismo". A realidade é que favelas e periferias são microcosmos de pluralidade ideológica, algo que assusta quem quer reduzir seres humanos a estereótipos.
Respostas aos Argumentos Esquerdistas (e Por que Falham)
"O pobre de direita é manipulado pela mídia!"
- Contradição: Se a mídia tradicional é dominada por elites (como alegam), por que grandes veículos são abertamente progressistas? A Record (evangélica) é exceção, não regra.
Contradição Central:
Como explicar que, segundo o Banco Mundial (2023), países com maior liberdade econômica (ex.: Chile, Polônia) reduziram a pobreza extrema em 60% nas últimas décadas, enquanto modelos estatizantes (ex.: Venezuela, Argentina com o governo peronista) afundaram na miséria? Simples: a esquerda prefere culpar o "neoliberalismo" a admitir que o pobre com o mínimo de consciência quer emprego, não esmola.Dado que Machuca:
- 71% das mulheres da periferia rejeitam o feminismo radical, associando-o a "prioridades distantes da realidade" (Instituto Locomotiva, 2023)."Ele vota contra os próprios interesses!"
- Falácia: Pressupõe que a esquerda define o que é o "interesse do pobre". Para um pai de família na Cidade de Deus, ter a boca de fogo fechada pode ser mais urgente que um aumento de 10% no Bolsa Família.
O pobre de direita não é uma anomalia. É o produto natural de um mundo complexo onde seres humanos têm aspirações, medos e valores diversos. Enquanto a esquerda insiste em tratá-lo como um projeto fracassado, ele está ocupado:
- Trabalhando para não depender do governo.
- Escolhendo religiões que dão sentido à sua vida.
- Rejeitando pautas identitárias que não resolvem o custo do gás de cozinha."É falta de educação política!"
- Ironia: Nos países nórdicos (modelo da esquerda), as classes baixas são as mais conservadoras. Educação não correlaciona com progressismo.
Por que o Debuste Precisa Acabar
A insistência em descredibilizar o pobre de direita revela um projeto de poder fracassado. A esquerda, ao substituir diálogo por deboche, perdeu a capacidade de representar quem mais precisaria dela. Enquanto isso, a direita — nem sempre por virtude, mas por pragmatismo — capturou o descontentamento de milhões com o status quo.
O pobre de direita existe porque ele não precisa da permissão do rico de esquerda para pensar. A incapacidade de entender isso só prova que a esquerda é a nova aristocracia.
Último Dado: Nas eleições de 2022, Tarcísio de Freitas (direita) venceu em 72% das favelas de São Paulo. O motivo? Seu discurso anti-burocracia e pró-microempreendedor.
A mensagem é clara: o pobre não é um projeto ideológico. É um agente político autônomo — e quem não entender isso continuará perdendo eleições.
A esquerda elitista não odeia o pobre de direita por ele ser "irracional". Odeia porque ele desafia o monopólio moral que ela construiu sobre a miséria alheia. Enquanto isso, o pobre segue sua vida, ignorando os berros de quem acha que sabem mais da sua vida que ele mesmo.
Pergunta Retórica (Para Incomodar):
Se a esquerda é tão sábia, por que não usa essa sabedoria para entender que pobre também cansa de ser tratado como cachorro que late no ritmo errado?
Fontes Citadas:
- Latinobarómetro (2022)
- IPEC (2023)
- USP (2021): "Segurança Pública e Percepções nas Favelas Cariocas"
- FGV (2020): "Informalidade e Tributação no Brasil"
- Datafolha (2023): "Perfil Religioso do Eleitorado Brasileiro"
- Atlas Intel (2022): "Autopercepção das Classes Baixas"
- Pew Research (2020): "Voting Patterns by Income in the U.S."
- TSE (2023): "Perfil Socioeconômico dos Filiados Partidários"
Leitura Recomendada para Esquerdistas:
- "Fome de Poder: Por que o Pobre Brasileiro Abandonou a Esquerda" (Fernando Schüller, 2023)
- "A Revolução dos Conservadores: Religião e Política nas Periferias" (Juliano Spyer, 2021)
- "Direita e Esquerda: Razões e Paixões" (Demétrio Magnoli, 2019) -
 @ bbb5dda0:f09e2747
2025-05-20 13:33:59
@ bbb5dda0:f09e2747
2025-05-20 13:33:59My week 19 started with a celebration of 80 years of liberation from the Germans (we love you guys now tho 🫶🏼). It feels conflicting, we're celebrating freedom, whilst cutting down those freedoms day by day more rapidly as time progresses. Should we still celebrate...?
The current path back to freedom can be mundane in the day to day but I wouldn't wanna have it any other way. These last couple weeks I've continued working on our TollGate pipelines to facilitate our release cycle, make it faster and easier to release in quick succession. There's been a lot of details to get right, because our releases are nostr based and once people start relying on the structure of the events we can't easily change it.
A TollGateOS release event now looks like this NIP-94 file metadata event:
json { "id": "a867f15ca7edc95a69e1557539a624466147584f68c62a16c47fe9bca3778312", "pubkey": "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a", "created_at": 1747475980, "kind": 1063, "tags": [ [ "url", "https://blossom.swissdash.site/9e5e8c48810a1b59cf10fa56486f311e048a0305eb58444992b6133fd19fcb3e.bin" ], [ "m", "application/octet-stream" ], [ "x", "9e5e8c48810a1b59cf10fa56486f311e048a0305eb58444992b6133fd19fcb3e" ], [ "ox", "9e5e8c48810a1b59cf10fa56486f311e048a0305eb58444992b6133fd19fcb3e" ], [ "architecture", "aarch64_cortex-a53" ], [ "device_id", "glinet_gl-mt3000" ], [ "supported_devices", "glinet,gl-mt3000 glinet,mt3000-snand" ], [ "openwrt_version", "24.10.1" ], [ "tollgate_os_version", "v0.0.2" ], [ "release_channel", "stable" ] ], "content": "TollGate OS Firmware for glinet_gl-mt3000", "sig": "1d050233428304685d202e954cb48714c800a7ca5f2d6a8d8fd657a775b9c51bf83364505311859c846e25098168a8ff309af2308712aafe634fcbdc96fcd84a" }One of the missing links was the
supported_devicestag. That is because the installer checks the device name by ssh-ing into the router and it returns theglinet,gl-mt3000which doesn't properly translate into thedevice_id, which is what's used for compiling the OS. So this helps us to do the lookups and compatibility checks in the installer.I also worked on: - getting the versioning of the tollgate-basic package's naming in line with the OpenWRT naming convention. - Rework versioning for dev builds into
[branchname].[commit_height].[commit_hash]which will show up on thedevrelease_channelreleases. - Getting an initial release of the tollgate-installer done, so we can easily flash a bunch of routers to become TollGates.Bright minds in Prague
I met up with some bright minds from the space in Prague where @cobrador and i did a workshop on turning routers into TollGates and start earning sats. As is part of building things, things break and people make us aware of issues that we wouldn't foresee. Like for some reason Minibits cashu tokens being rejected, which is likely because of the memo's but we still need to dive into that issue.
Also we released [v0.0.2] of TollGate OS, which now includes an updater feature, again for faster release cycles. Currently we're focussing on getting a v0.0.3 out quickly with fixes for the user feedback we've gathered so far!
Receipt.Cash
I also, kind of unplanned, saw an opportunity to shill Receipt.Cash. I'd made a few improvements recently and it's ready enough for reckless people to try it out ;).
|
 |
| 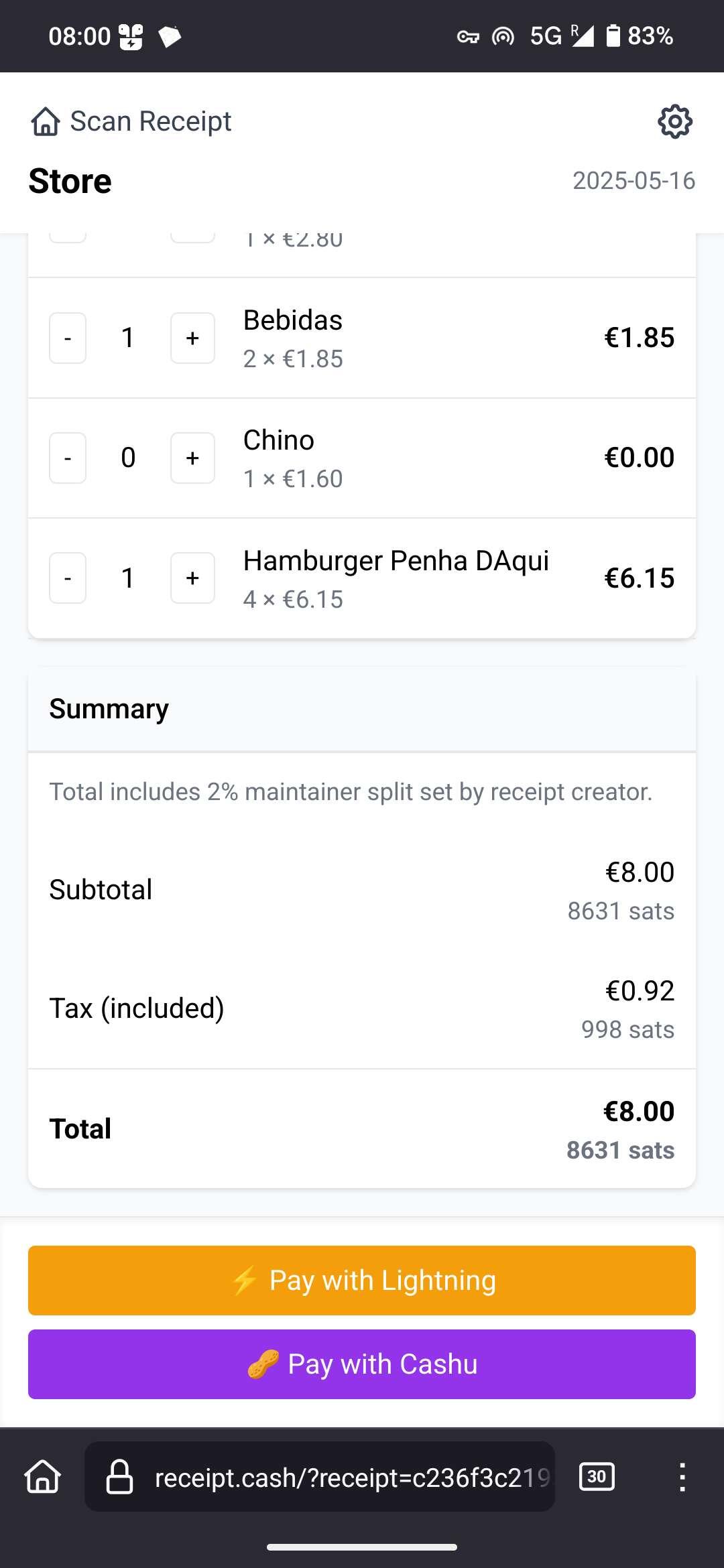 |
| |
| Payer Scans any fiat receipt & Share link with friends | Friends tap what they had, price is auto-converted to sats, then pay by Lightning or Cashu. |
If you want to try it, BE CAREFUL! It is highly experimental and you might lose your sats, no refunds!
|
| |
| Payer Scans any fiat receipt & Share link with friends | Friends tap what they had, price is auto-converted to sats, then pay by Lightning or Cashu. |
If you want to try it, BE CAREFUL! It is highly experimental and you might lose your sats, no refunds!Source Code here.
-
 @ 3770c235:16042bcc
2025-05-20 13:27:03
@ 3770c235:16042bcc
2025-05-20 13:27:03In recent years, a remarkable transformation has taken place in the way people view and utilize their homes. No longer confined to the four walls of traditional interior spaces, homeowners are increasingly turning their attention outward—toward their own backyards. The concept of outdoor living has evolved from mere patio furniture and barbecues to fully functional living environments, equipped with kitchens, entertainment systems, and even workspaces.
This growing trend is not just a design choice; it reflects changing lifestyles, shifting priorities, and a reimagining of what it means to feel at home. The rise of outdoor living is more than a fad—it's a movement, and it's here to stay.
**A Shift in Lifestyle and Values ** At the heart of the outdoor living boom is a deeper shift in how people value their time, environment, and personal space. The COVID-19 pandemic played a significant role in this evolution. Lockdowns and restrictions forced many to reassess their living situations, seeking ways to make the most of what they already had. The backyard, once overlooked, suddenly became a sanctuary—a space to breathe, gather, and escape the monotony of indoor life.
According to a 2021 study by the International Casual Furnishings Association, over 90% of Americans with outdoor living space report that it is more valuable to them than ever before, with nearly 60% saying they upgraded their outdoor spaces during the pandemic source.
This change in perception is not solely pandemic-related. There's a growing emphasis on wellness, mindfulness, and balance. People are looking to nature for inspiration and relaxation. Outdoor living spaces—be they modest balconies or expansive decks—allow homeowners to connect with nature without leaving the comfort of home.
Redefining the Backyard: From Playgrounds to Living Rooms
Traditionally, the backyard has served specific purposes—gardening, children’s play areas, maybe a grill tucked in the corner. Today, backyards are being reimagined as multi-functional extensions of the home.
-
Outdoor Kitchens and Dining Areas Once considered a luxury, outdoor kitchens have become increasingly common. With built-in grills, pizza ovens, refrigerators, sinks, and full countertops, these outdoor culinary spaces rival their indoor counterparts. The convenience of preparing and serving meals outside is matched by the social benefit: cooking becomes a shared experience.
-
Living and Lounge Areas Outdoor seating now goes far beyond foldable lawn chairs. Modular sectionals, fire pits, weather-resistant rugs, and even smart lighting have turned patios into legitimate living rooms under the sky. Some include mounted TVs, Bluetooth speakers, and retractable canopies or pergolas for all-weather comfort.
-
Work and Study Zones Remote work has blurred the boundaries between office and home. Now, it’s expanding into the outdoors. With Wi-Fi extenders, weather-protected furniture, and shade structures, backyards are becoming viable home office environments, perfect for Zoom calls with a natural backdrop.
-
Wellness Retreats From hot tubs and saunas to yoga decks and meditation gardens, outdoor spaces are being tailored to support wellness. These personal sanctuaries offer solitude and stress relief, all within the perimeter of one's property.
The Role of Technology and Innovation Modern outdoor spaces owe much of their versatility to advances in technology and materials. Weather-resistant fabrics, composite decking, solar lighting, and smart irrigation systems have all expanded what's possible in backyard design.
Smart home technology has also made its way outdoors. Lighting can be automated or voice-controlled. Outdoor speakers can be synced across zones. Even grills can be connected to apps that monitor cooking temperatures. These innovations allow outdoor living to be both luxurious and convenient, requiring minimal maintenance while offering maximum comfort.
**Economic Impact and Value Addition ** Investing in outdoor living isn't just about lifestyle—it’s also smart economics. Outdoor upgrades can significantly boost a home's resale value. A well-designed patio or outdoor kitchen can yield a return on investment (ROI) of up to 80%, according to the National Association of Realtors. In fact, data from Houzz shows that nearly 57% of homeowners are investing in their outdoor spaces specifically to increase resale value source.
This financial motivation has fueled demand for landscape architects, outdoor furniture designers, and construction professionals specializing in outdoor living projects. As a result, the industry surrounding outdoor enhancements—from pergola manufacturers to luxury fire pit designers—has seen exponential growth.
Environmental Considerations and Sustainability As outdoor living becomes more popular, so does the demand for environmentally conscious design. Homeowners are increasingly incorporating sustainable elements into their outdoor plans, including: • Native plant landscaping: Reduces water usage and supports local ecosystems. • Rainwater harvesting systems: Collect and store rain for garden irrigation. • Solar-powered lighting: Minimizes energy consumption while maximizing ambiance. • Permeable paving materials: Reduce runoff and promote groundwater recharge. Green living isn't just a buzzword—it’s influencing how people design their outdoor sanctuaries. Eco-conscious homeowners are prioritizing sustainability as much as aesthetics, ensuring their outdoor spaces are in harmony with nature, not in conflict with it.
The Social Connection
Outdoor living also taps into our basic need for connection. From summer barbecues to cozy firepit gatherings, the backyard is an ideal setting for meaningful social interactions. During a time when indoor gatherings have been restricted or limited, outdoor spaces have offered a safer, more accessible alternative.
Community ties can also be strengthened through outdoor living. In urban settings, rooftop terraces or shared gardens create communal spaces for neighbors to engage, collaborate, and unwind. For families, these outdoor extensions offer a way to spend quality time together—whether through games, meals, or simply enjoying the open air. For individuals, they provide a space to recharge, free from the digital and physical clutter of indoor life.
Customization and Personalization
One of the most appealing aspects of outdoor living is the high degree of customization available. Unlike interior spaces that may be limited by architectural constraints, outdoor areas can often be more flexible in layout and design.
Homeowners can craft outdoor environments that reflect their personalities and values: • The entertainer may opt for a bar area, ambient lighting, and surround sound. • The minimalist might choose clean lines, neutral tones, and eco-friendly materials. • The nature-lover may emphasize greenery, water features, and natural textures. DIY options also abound, allowing for creative freedom and budget-friendly upgrades. Raised garden beds, handmade furniture, repurposed materials, and vertical planters give individuals the opportunity to leave their personal mark on the space.
The Influence of Global Design Trends Outdoor living isn’t confined to North America. Around the world, cultures have long embraced outdoor spaces—from Japanese zen gardens to Mediterranean courtyards. The current global design conversation draws inspiration from a variety of traditions and climates.
Scandinavian principles of simplicity and functionality influence clean-lined, open-air designs, while tropical resorts have inspired lush, greenery-filled retreats in suburban settings. The blending of international styles enables homeowners to create outdoor spaces that are both eclectic and functional.
Looking Ahead: The Future of Outdoor Living The trajectory of outdoor living points to continued growth, innovation, and integration. Here are some trends likely to define the next decade:
- Year-Round Use With heating lamps, insulated pergolas, and all-weather furniture, outdoor spaces are becoming viable in all seasons. Expect to see more designs tailored for winter, including hot tubs, enclosed lounges, and warm lighting features.
- Outdoor Smart Hubs Technology will play an even greater role, with integrated outdoor control systems for lighting, security, irrigation, and entertainment—managed through a single device or app.
- Edible Landscaping Gardens will not only be for beauty but also for sustenance. Raised vegetable beds, fruit trees, and herb walls will become staples in functional outdoor design.
- Modular Design Portable and adaptable elements like movable walls, foldable furniture, and hybrid indoor-outdoor structures will offer more flexibility, especially in smaller spaces.
- Wellness Integration Expect an even stronger emphasis on health and well-being—cold plunge pools, outdoor gyms, meditation pods, and immersive natural soundscapes will take center stage.
Conclusion The rise of outdoor living is not just a design phenomenon—it’s a cultural shift. Homeowners are recognizing the value of outdoor spaces as extensions of their identities, routines, and dreams. Whether it's a serene garden, a vibrant entertainment hub, or a cozy work nook, the backyard is being redefined as a vital part of the home. In a world that often feels fast-paced and digitally overloaded, outdoor living offers a much-needed antidote: space to breathe, relax, connect, and thrive. It’s about more than upgrading the home—it’s about enhancing the human experience. As this trend continues to evolve, one thing is clear: the best room in the house may not be inside at all.
-
-
 @ 04c915da:3dfbecc9
2025-03-07 00:26:37
@ 04c915da:3dfbecc9
2025-03-07 00:26:37There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ 6e0ea5d6:0327f353
2025-02-21 18:15:52
@ 6e0ea5d6:0327f353
2025-02-21 18:15:52"Malcolm Forbes recounts that a lady, wearing a faded cotton dress, and her husband, dressed in an old handmade suit, stepped off a train in Boston, USA, and timidly made their way to the office of the president of Harvard University. They had come from Palo Alto, California, and had not scheduled an appointment. The secretary, at a glance, thought that those two, looking like country bumpkins, had no business at Harvard.
— We want to speak with the president — the man said in a low voice.
— He will be busy all day — the secretary replied curtly.
— We will wait.
The secretary ignored them for hours, hoping the couple would finally give up and leave. But they stayed there, and the secretary, somewhat frustrated, decided to bother the president, although she hated doing that.
— If you speak with them for just a few minutes, maybe they will decide to go away — she said.
The president sighed in irritation but agreed. Someone of his importance did not have time to meet people like that, but he hated faded dresses and tattered suits in his office. With a stern face, he went to the couple.
— We had a son who studied at Harvard for a year — the woman said. — He loved Harvard and was very happy here, but a year ago he died in an accident, and we would like to erect a monument in his honor somewhere on campus.— My lady — said the president rudely —, we cannot erect a statue for every person who studied at Harvard and died; if we did, this place would look like a cemetery.
— Oh, no — the lady quickly replied. — We do not want to erect a statue. We would like to donate a building to Harvard.
The president looked at the woman's faded dress and her husband's old suit and exclaimed:
— A building! Do you have even the faintest idea of how much a building costs? We have more than seven and a half million dollars' worth of buildings here at Harvard.
The lady was silent for a moment, then said to her husband:
— If that’s all it costs to found a university, why don’t we have our own?
The husband agreed.
The couple, Leland Stanford, stood up and left, leaving the president confused. Traveling back to Palo Alto, California, they established there Stanford University, the second-largest in the world, in honor of their son, a former Harvard student."
Text extracted from: "Mileumlivros - Stories that Teach Values."
Thank you for reading, my friend! If this message helped you in any way, consider leaving your glass “🥃” as a token of appreciation.
A toast to our family!
-
 @ 9e69e420:d12360c2
2025-02-17 17:12:01
@ 9e69e420:d12360c2
2025-02-17 17:12:01President Trump has intensified immigration enforcement, likening it to a wartime effort. Despite pouring resources into the U.S. Immigration and Customs Enforcement (ICE), arrest numbers are declining and falling short of goals. ICE fell from about 800 daily arrests in late January to fewer than 600 in early February.
Critics argue the administration is merely showcasing efforts with ineffectiveness, while Trump seeks billions more in funding to support his deportation agenda. Increased involvement from various federal agencies is intended to assist ICE, but many lack specific immigration training.
Challenges persist, as fewer immigrants are available for quick deportation due to a decline in illegal crossings. Local sheriffs are also pressured by rising demands to accommodate immigrants, which may strain resources further.
-
 @ 472f440f:5669301e
2025-05-20 13:01:09
@ 472f440f:5669301e
2025-05-20 13:01:09Marty's Bent

via me
Don't sleep on what's happening in Japan right now. We've been covering the country and the fact that they've lost control of their yield curve since late last year. After many years of making it a top priority from a monetary policy perspective, last year the Bank of Japan decided to give up on yield curve control in an attempt to reel inflation. This has sent yields for the 30-year and 40-year Japanese government bonds to levels not seen since the early 2000s in the case of the 30-year and levels never before seen for the 40-year, which was launched in 2007. With a debt to GDP ratio that has surpassed 250% and a population that is aging out with an insufficient amount of births to replace the aging workforce, it's hard to see how Japan can get out of this conundrum without some sort of economic collapse.
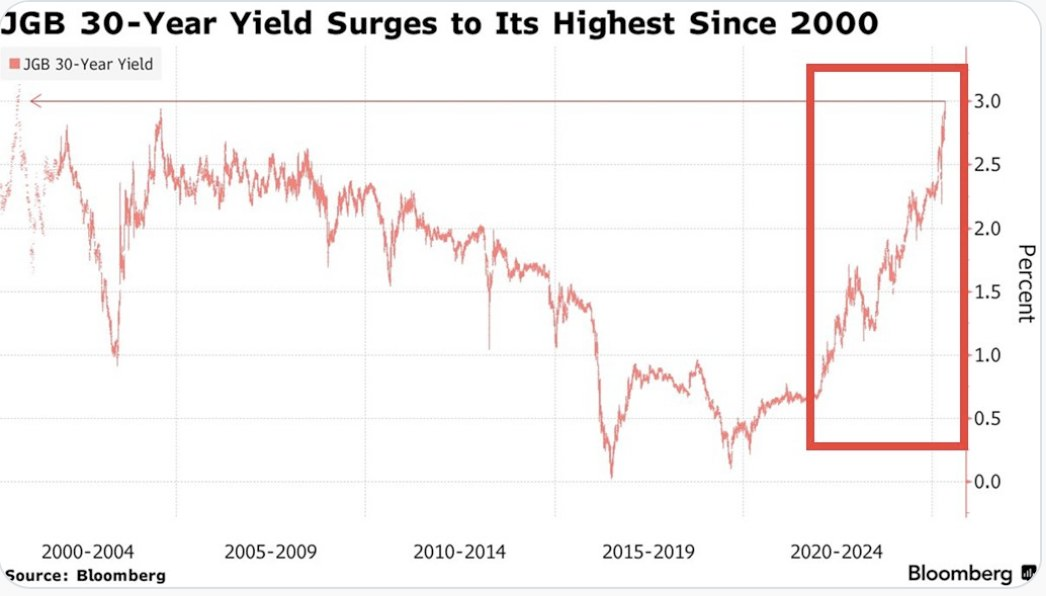

This puts the United States in a tough position considering the fact that Japan is one of the largest holders of U.S. Treasury bonds with more than 1,135 sats | $1.20 trillion in exposure. If things get too out of control in Japan and the yield curve continues to drift higher and inflation continues to creep higher Japan can find itself in a situation where it's a forced seller of US Treasuries as they attempt to strengthen the yen. Another aspect to consider is the fact that investors may see the higher yields on Japanese government bonds and decide to purchase them instead of US Treasuries. This is something to keep an eye on in the weeks to come. Particularly if higher rates drive a higher cost of capital, which leads to even more inflation. As producers are forced to increase their prices to ensure that they can manage their debt repayments.
It's never a good sign when the Japanese Prime Minister is coming out to proclaim that his country's financial situation is worse than Greece's, which has been a laughing stock of Europe for the better part of three decades. Japan is a very proud nation, and the fact that its Prime Minister made a statement like this should not be underappreciated.
As we noted last week, the 10-year and 30-year U.S. Treasury bonds are drifting higher as well. Earlier today, the 30-year bond yield surpassed 5%, which has been a psychological level that many have been pointed to as a critical tipping point. When you take a step back and look around the world it seems pretty clear that bond markets are sending a very strong signal. And that signal is that something is not well in the back end of the financial system.
This is even made clear when you look at the private sector, particularly at consumer debt. In late March, we warned of the growing trend of buy now, pay later schemes drifting down market as major credit card companies released charge-off data which showed charge-off rates reaching levels not seen since the 2008 great financial crisis. At the time, we could only surmise that Klarna was experiencing similar charge-off rates on the bigger-ticket items they financed and started doing deals with companies like DoorDash to finance burrito deliveries in an attempt to move down market to finance smaller ticket items with a higher potential of getting paid back. It seems like that inclination was correct as Klarna released data earlier today showing more losses on their book as consumers find it extremely hard to pay back their debts.

via NewsWire
This news hit the markets on the same day as the average rate of the 30-year mortgage in the United States rose to 7.04%. I'm not sure if you've checked lately, but real estate prices are still relatively elevated outside of a few big cities who expanded supply significantly during the COVID era as people flooded out of blue states towards red states. It's hard to imagine that many people can afford a house based off of sticker price alone, but with a 7% 30-year mortgage rate it's becoming clear that the ability of the Common Man to buy a house is simply becoming impossible.
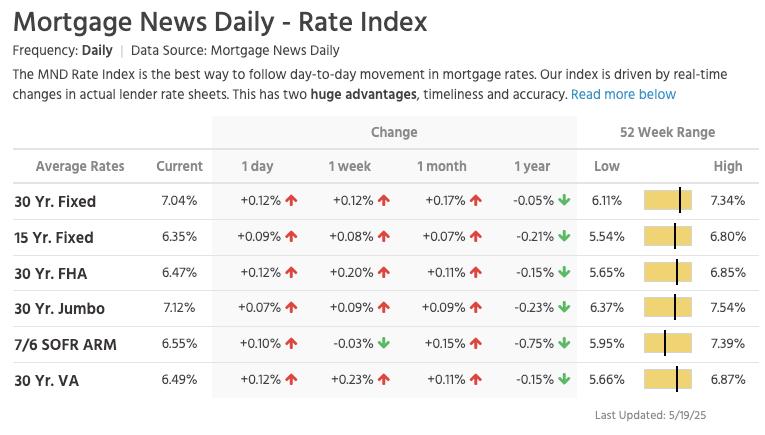
via Lance Lambert
The mortgage rate data is not the only thing you need to look at to understand that it's becoming impossible for the Common Man of working age to buy a house. New data has recently been released that highlights That the median home buyer in 2007 was born in 1968, and the median home buyer in 2024 was born in 1968. Truly wild when you think of it. As our friend Darth Powell cheekily highlights below, we find ourselves in a situation where boomers are simply trading houses and the younger generations are becoming indentured slaves. Forever destined to rent because of the complete inability to afford to buy a house.
via Darth Powell
via Yahoo Finance
Meanwhile, Bitcoin re-approached all-time highs late this evening and looks primed for another breakout to the upside. This makes sense if you're paying attention. The high-velocity trash economy running on an obscene amount of debt in both the public and private sectors seems to be breaking at the seams. All the alarm bells are signaling that another big print is coming. And if you hope to preserve your purchasing power or, ideally, increase it as the big print approaches, the only thing that makes sense is to funnel your money into the hardest asset in the world, which is Bitcoin.

via Bitbo
Buckle up, freaks. It's gonna be a bumpy ride. Stay humble, Stack Sats.
Trump's Middle East Peace Strategy: Redefining U.S. Foreign Policy
In his recent Middle East tour, President Trump signaled what our guest Dr. Anas Alhajji calls "a major change in US policy." Trump explicitly rejected the nation-building strategies of his predecessors, contrasting the devastation in Afghanistan and Iraq with the prosperity of countries like Saudi Arabia and UAE. This marks a profound shift from both Republican and Democratic foreign policy orthodoxy. As Alhajji noted, Trump's willingness to meet with Syrian President Assad follows a historical pattern where former adversaries eventually become diplomatic partners.
"This is really one of the most important shifts in US foreign policy to say, look, sorry, we destroyed those countries because we tried to rebuild them and it was a big mistake." - Dr. Anas Alhajji
The administration's new approach emphasizes negotiation over intervention. Rather than military solutions, Trump is engaging with groups previously considered off-limits, including the Houthis, Hamas, and Iran. This pragmatic stance prioritizes economic cooperation and regional stability over ideological confrontation. The focus on trade deals and investment rather than regime change represents a fundamental reimagining of America's role in the Middle East.
Check out the full podcast here for more on the Iran nuclear situation, energy market predictions, and why AI development could create power grid challenges. Only on TFTC Studio.
Headlines of the Day
Bitcoin Soars to 100,217 sats | $106.00K While Bonds Lose 40% Since 2020 - via X
US Senate Advances Stablecoin Bill As America Embraces Bitcoin - via X
Get our new STACK SATS hat - via tftcmerch.io
Texas House Debates Bill For State-Run Bitcoin Reserve - via X
Take the First Step Off the Exchange
Bitkey is an easy, secure way to move your Bitcoin into self-custody. With simple setup and built-in recovery, it’s the perfect starting point for getting your coins off centralized platforms and into cold storage—no complexity, no middlemen.
Take control. Start with Bitkey.
Use the promo code “TFTC20” during checkout for 20% off
Ten31, the largest bitcoin-focused investor, has deployed 158,469 sats | $150.00M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/invest.
Final thought...
Don't let the noise consume you. Focus on making your life 1% better every day.
Get this newsletter sent to your inbox daily: https://www.tftc.io/bitcoin-brief/
Subscribe to our YouTube channels and follow us on Nostr and X:
-
 @ fd208ee8:0fd927c1
2025-02-15 07:37:01
@ fd208ee8:0fd927c1
2025-02-15 07:37:01E-cash are coupons or tokens for Bitcoin, or Bitcoin debt notes that the mint issues. The e-cash states, essentially, "IoU 2900 sats".
They're redeemable for Bitcoin on Lightning (hard money), and therefore can be used as cash (softer money), so long as the mint has a good reputation. That means that they're less fungible than Lightning because the e-cash from one mint can be more or less valuable than the e-cash from another. If a mint is buggy, offline, or disappears, then the e-cash is unreedemable.
It also means that e-cash is more anonymous than Lightning, and that the sender and receiver's wallets don't need to be online, to transact. Nutzaps now add the possibility of parking transactions one level farther out, on a relay. The same relays that cannot keep npub profiles and follow lists consistent will now do monetary transactions.
What we then have is * a transaction on a relay that triggers * a transaction on a mint that triggers * a transaction on Lightning that triggers * a transaction on Bitcoin.
Which means that every relay that stores the nuts is part of a wildcat banking system. Which is fine, but relay operators should consider whether they wish to carry the associated risks and liabilities. They should also be aware that they should implement the appropriate features in their relay, such as expiration tags (nuts rot after 2 weeks), and to make sure that only expired nuts are deleted.
There will be plenty of specialized relays for this, so don't feel pressured to join in, and research the topic carefully, for yourself.
https://github.com/nostr-protocol/nips/blob/master/60.md https://github.com/nostr-protocol/nips/blob/master/61.md
-
 @ 88cc134b:5ae99079
2025-05-20 12:22:03
@ 88cc134b:5ae99079
2025-05-20 12:22:03content
nostr:nevent1qvzqqqqqqypzpkygz22lv3pdey6gr7ygmk67wjh24hdvj3t797mm6z0x3ax4erdhqqsdxy48qm3tces0tu90shwltcg20zsprejkahklwftpzyhytcf32tc9sm779
-
 @ a296b972:e5a7a2e8
2025-05-20 12:22:00
@ a296b972:e5a7a2e8
2025-05-20 12:22:00Die Natur strebt nach einem Gleichgewicht durch Ausgleich von nicht zueinander passenden Verhältnissen. Die Gesellschaft ist ein sozialer Organismus, der ebenso nach Ausgleich und einer Stimmigkeit der Verhältnisse strebt. Das sind Naturgesetze, die keine Regierung auf Dauer imstande ist, außer Kraft zu setzen.
Weder oppositionelle Kräfte, noch Kräfte innerhalb des Souveräns haben die Absicht, die Demokratie abzuschaffen. Es geht vielmehr darum, sie wieder in der Form herzustellen, in der sie ihren Namen auch verdient. Dazu gehört, dass alle Macht vom Volke ausgeht, was derzeit nicht der Fall ist.
Ein durch den Staat vorgegebenes Bildungssystem hat Menschen vor allem zu gefügigen Rädchen im Wirtschaftsgetriebe und nicht zu alles kritisch hinterfragenden Bürgern erzogen, die ständig der Regierung auf die Finger schauen.
Wenn die Bürger, der Souverän, eine Regierung immer mehr „machen lässt“ und glaubt, es sei genug, alle 4 Jahre sein Wahl-Kreuzchen zu machen, entfernt er sich immer mehr von der Kontrolle der durch ihn beauftragten Vertreter, und diese entfernen sich so immer mehr vom Alltag der Bürger.
Zu wenig Gegenrede des Souveräns führt zu immer mehr Übermut der Regierung, die sich immer sicherer wird, mit jedem Unsinn durchzukommen.
Ist dann die Schmerzgrenze des Souveräns erreicht, beginnt er, die Opposition zu stärken. In einer funktionierenden Demokratie würde das dazu führen, dass die Opposition die Regierung bildet, die dann die Chance hat, Fehlentwicklungen abzustellen und ausgleichend tätig zu werden.
Derzeit findet sowohl beim Souverän, als auch bei den Parteien, die bisher Regierungen zusammengestellt haben, ein Erwachen statt.
Da die ehemaligen Volks-Parteien unbedingt an der Macht festhalten wollen, seitens des Souveräns auf zu wenig Widerstand stoßen, wird mit der Macht, einer Demokratie nicht würdig, umgegangen. Dem sollte dringend Einhalt geboten werden.
Der Missbrauch äußert sich in brutalen (Lieblingswort der Ex-Außen-Dings) Einschränkungen der Grundrechte (Corona-Zeit), in der Einschränkung der Meinungsfreiheit (D S A), in Tendenzen zunehmender Kontrolle und Überwachung, Förderung von Denunzianten-Portalen, Kapern des öffentlich-rechtlichen Rundfunks, Förderung von NGOs, die als Sprechpuppen genutzt werden. Besetzt von Menschen, die entweder tatsächlich überzeugt sind von dem, was sie ideologisch vertreten, oder die über Charaktereigenschaften verfügen, die noch sehr viel Optimierungspotenzial in sich bergen. Gepaart mit fachlicher Inkompetenz ist das ein gefährlicher Cocktail.
Erst jüngst sogar durch Ausreiseverbote, wie in einem Staat, mit dem man das derzeitige Deutschland nicht vergleichen darf. So groß ist inzwischen schon die Angst geworden, die Kontrolle über die Macht zu verlieren. Alles, was an Kritik geäußert werden will, gilt als Delegitimierung des Staates. Auf keinen Fall darf sie im Ausland geäußert werden, damit es ja nichts davon mitbekommt, was in Deutschland abgeht. Das ist so wie ein Kind, dass sich die Hände vor die Augen hält und meint, es würde nicht gesehen werden.
Die Regierung ist übergriffig geworden. Je lauter sie Demokratie schreit, desto totalitärer wird sie.
Durch fehlende Kontrolle des Souveräns sind charakterlich und fachlich ungeeignete Personen in die Politik gelangt, deren ständige Überforderung dazu führt, dass sich deren Entscheidungen immer weiter von der Lebensrealität des Souveräns entfernen.
Bislang haben rund 25% des Souveräns diese Schieflage erkannt und wollen einer Opposition, die so stark geworden ist, weil die Alt-Parteien über Jahre Fehler an Fehler aneinandergereiht haben, die Gelegenheit geben, diese Fehler zu beheben und auszugleichen. Offen bleibt die Frage, ob sie dazu wirklich in der Lage sind, oder ob die Gefahr besteht, dass sie von einem möglicherweise grundsätzlich kranken System vereinnahmt werden.
Da es seitens der Alt-Parteien keine Einsicht gibt, dass sie in der Regierung nicht mehr den Willen des Souveräns vertreten, derzeit auch besonders gut zu sehen an dem Friedenswillen des Souveräns im Vergleich zur Kriegstreiberei der Regierung, bleibt nur, der Opposition zumindest die Chance zu geben, es besser zu machen und den Willen des Souveräns umzusetzen. Gelänge das nicht, ist die Demokratie, wie wir sie bislang verstanden haben, gescheitert.
Eine daraus resultierende Staatsform stünde dem Freiheitsgedanken diametral gegenüber.
Die Verteidigung von Unseredemokratie seitens der Regierung entlarvt das eigentliche, was damit gemeint ist, nämlich die Erhaltung der eigenen Macht, verbunden mit allen Vorzügen und Privilegien. Sie richtet sich gegen das eigene Volk, das mit einer ganz normal funktionierenden Demokratie schon sehr zufrieden wäre. Unseredemokratie ist nicht unsere Demokratie!
In Anlehnung an die berühmt gewordene Lüge Walter Ulbrichs: „Niemand hat die Absicht eine Mauer zu errichten“, hat derzeit niemand die Absicht, die sogenannte Brandmauer einzureißen, bzw. sie so lange stehen zu lassen, wie es eben geht, um die herrschenden Machtverhältnisse so lange wie möglich aufrechtzuerhalten. Die Geschichte hat jedoch zum Glück gezeigt, dass selbst eine Berliner Mauer nicht ewig hält.
Wie sich aus dem absurd-lächerlichen Gutachten, einer der Regierung gegenüber weisungsgebundenen Behörde herausgestellt hat, gibt es keinerlei Anzeichen dafür, dass die Opposition die demokratische Grundordnung weder gefährden noch beseitigen will.
Da die ehemaligen Volksparteien augenscheinlich nicht in der Lage sind, politische, wirtschaftliche und gesellschaftliche Verhältnisse zum Wohle des Deutschen Volkes herzustellen, ist der demokratische Weg, die Opposition hierzu zu ermächtigen.
Wird das weiterhin verhindert, wird der Unmut des Souveräns weiter zunehmen, und spätestens, wenn die zunehmenden Schikanen die Schmerzgrenze überschritten haben, wird der Souverän nach geeigneten Mitteln und Möglichkeiten suchen, diese Schieflage zu beheben und auszugleichen.
Derzeit stehen sich ein in der Zahl und im Befinden zunehmend unzufrieden werdender Souverän und eine immer absurdere Entscheidungen treffende Regierung im lebendigen Tauziehen um Interessen gegenüber. Je mehr Bockmist die Alt-Parteien bauen, um so stärker wird die Opposition.
Aufgrund der jetzt schon vorhandenen Anzahl wacher Bürger und der Anzahl der in der Politik Unfähigen, ist eigentlich schon jetzt klar, wer in diesem Tauziehen die größere Kraft hat und wer das „Spiel“ nach demokratischen Regeln am Ende gewinnen wird. Das ist eindeutig der Souverän. Verliert er, wider Erwarten, verliert auch die Demokratie.
Dem Souverän fehlt nur noch ein wenig mehr Selbstvertrauen und ein Bewusstsein für die Macht, über die er tatsächlich verfügt.
Je mehr absurde Entscheidungen seitens der Regierung getroffen werden, und man arbeitet ja sehr fleißig daran, besonders, wenn es um Frieden geht, desto stärker wird das Selbstbewusstsein des Souveräns werden und ein natürlicher, friedlicher Ausgleich der Schieflage kann stattfinden. Der Start der neuen Regierung war jedenfalls schon einmal sehr "Keine-4-Jahre".
Wer sich in die steile und eisglatte Abfahrtspiste Deutschlands vertiefen will, hier eine Rezension zu dem Buch „Im Taumel des Niedergangs“ von dem von mir sehr geschätzten und akribisch arbeitenden Uwe Froschauer:
https://www.manova.news/artikel/abwarts
oder
Dieser Artikel wurde mit dem Pareto-Client geschrieben
* *
(Bild von pixabay)
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-20 13:39:22
@ 5d4b6c8d:8a1c1ee3
2025-05-20 13:39:22https://youtu.be/US9iYJNTOkU
I had no idea Tosh was still doing anything, much less that he talks about sports.
https://stacker.news/items/984547
-
 @ 0fa80bd3:ea7325de
2025-02-14 23:24:37
@ 0fa80bd3:ea7325de
2025-02-14 23:24:37intro
The Russian state made me a Bitcoiner. In 1991, it devalued my grandmother's hard-earned savings. She worked tirelessly in the kitchen of a dining car on the Moscow–Warsaw route. Everything she had saved for my sister and me to attend university vanished overnight. This story is similar to what many experienced, including Wences Casares. The pain and injustice of that time became my first lessons about the fragility of systems and the value of genuine, incorruptible assets, forever changing my perception of money and my trust in government promises.
In 2014, I was living in Moscow, running a trading business, and frequently traveling to China. One day, I learned about the Cypriot banking crisis and the possibility of moving money through some strange thing called Bitcoin. At the time, I didn’t give it much thought. Returning to the idea six months later, as a business-oriented geek, I eagerly began studying the topic and soon dove into it seriously.
I spent half a year reading articles on a local online journal, BitNovosti, actively participating in discussions, and eventually joined the editorial team as a translator. That’s how I learned about whitepapers, decentralization, mining, cryptographic keys, and colored coins. About Satoshi Nakamoto, Silk Road, Mt. Gox, and BitcoinTalk. Over time, I befriended the journal’s owner and, leveraging my management experience, later became an editor. I was drawn to the crypto-anarchist stance and commitment to decentralization principles. We wrote about the economic, historical, and social preconditions for Bitcoin’s emergence, and it was during this time that I fully embraced the idea.
It got to the point where I sold my apartment and, during the market's downturn, bought 50 bitcoins, just after the peak price of $1,200 per coin. That marked the beginning of my first crypto winter. As an editor, I organized workflows, managed translators, developed a YouTube channel, and attended conferences in Russia and Ukraine. That’s how I learned about Wences Casares and even wrote a piece about him. I also met Mikhail Chobanyan (Ukrainian exchange Kuna), Alexander Ivanov (Waves project), Konstantin Lomashuk (Lido project), and, of course, Vitalik Buterin. It was a time of complete immersion, 24/7, and boundless hope.
After moving to the United States, I expected the industry to grow rapidly, attended events, but the introduction of BitLicense froze the industry for eight years. By 2017, it became clear that the industry was shifting toward gambling and creating tokens for the sake of tokens. I dismissed this idea as unsustainable. Then came a new crypto spring with the hype around beautiful NFTs – CryptoPunks and apes.
I made another attempt – we worked on a series called Digital Nomad Country Club, aimed at creating a global project. The proceeds from selling images were intended to fund the development of business tools for people worldwide. However, internal disagreements within the team prevented us from completing the project.
With Trump’s arrival in 2025, hope was reignited. I decided that it was time to create a project that society desperately needed. As someone passionate about history, I understood that destroying what exists was not the solution, but leaving everything as it was also felt unacceptable. You can’t destroy the system, as the fiery crypto-anarchist voices claimed.
With an analytical mindset (IQ 130) and a deep understanding of the freest societies, I realized what was missing—not only in Russia or the United States but globally—a Bitcoin-native system for tracking debts and financial interactions. This could return control of money to ordinary people and create horizontal connections parallel to state systems. My goal was to create, if not a Bitcoin killer app, then at least to lay its foundation.
At the inauguration event in New York, I rediscovered the Nostr project. I realized it was not only technologically simple and already quite popular but also perfectly aligned with my vision. For the past month and a half, using insights and experience gained since 2014, I’ve been working full-time on this project.
-
 @ e3ba5e1a:5e433365
2025-02-13 06:16:49
@ e3ba5e1a:5e433365
2025-02-13 06:16:49My favorite line in any Marvel movie ever is in “Captain America.” After Captain America launches seemingly a hopeless assault on Red Skull’s base and is captured, we get this line:
“Arrogance may not be a uniquely American trait, but I must say, you do it better than anyone.”
Yesterday, I came across a comment on the song Devil Went Down to Georgia that had a very similar feel to it:

America has seemingly always been arrogant, in a uniquely American way. Manifest Destiny, for instance. The rest of the world is aware of this arrogance, and mocks Americans for it. A central point in modern US politics is the deriding of racist, nationalist, supremacist Americans.
That’s not what I see. I see American Arrogance as not only a beautiful statement about what it means to be American. I see it as an ode to the greatness of humanity in its purest form.
For most countries, saying “our nation is the greatest” is, in fact, twinged with some level of racism. I still don’t have a problem with it. Every group of people should be allowed to feel pride in their accomplishments. The destruction of the human spirit since the end of World War 2, where greatness has become a sin and weakness a virtue, has crushed the ability of people worldwide to strive for excellence.
But I digress. The fears of racism and nationalism at least have a grain of truth when applied to other nations on the planet. But not to America.
That’s because the definition of America, and the prototype of an American, has nothing to do with race. The definition of Americanism is freedom. The founding of America is based purely on liberty. On the God-given rights of every person to live life the way they see fit.
American Arrogance is not a statement of racial superiority. It’s barely a statement of national superiority (though it absolutely is). To me, when an American comments on the greatness of America, it’s a statement about freedom. Freedom will always unlock the greatness inherent in any group of people. Americans are definitionally better than everyone else, because Americans are freer than everyone else. (Or, at least, that’s how it should be.)
In Devil Went Down to Georgia, Johnny is approached by the devil himself. He is challenged to a ridiculously lopsided bet: a golden fiddle versus his immortal soul. He acknowledges the sin in accepting such a proposal. And yet he says, “God, I know you told me not to do this. But I can’t stand the affront to my honor. I am the greatest. The devil has nothing on me. So God, I’m gonna sin, but I’m also gonna win.”
Libertas magnitudo est
-
 @ dda7ca19:5811f8cd
2025-02-11 12:28:20
@ dda7ca19:5811f8cd
2025-02-11 12:28:20test
-
 @ 91bea5cd:1df4451c
2025-05-20 12:16:57
@ 91bea5cd:1df4451c
2025-05-20 12:16:57Contexto e início
O precursor direto do avivamento foi William J. Seymour, um pregador afro-americano filho de ex-escravos, influenciado pelos ensinamentos de Charles Parham, que pregava o "batismo no Espírito Santo" com evidência do falar em línguas.
Em 1906, Seymour foi convidado para pregar em uma igreja em Los Angeles. Após ser rejeitado por alguns por sua pregação sobre o batismo com o Espírito Santo, ele começou a liderar reuniões de oração na casa da família Asberry. Em abril de 1906, durante uma dessas reuniões, os participantes começaram a experimentar manifestações intensas do Espírito Santo, incluindo glossolalia (falar em línguas), curas e profecias.
A Rua Azusa
Logo, o número de participantes cresceu tanto que foi necessário mudar para um antigo prédio da Igreja Metodista Africana Episcopal, no número 312 da Rua Azusa, no centro de Los Angeles. Esse local se tornou o epicentro do avivamento.
Características marcantes
Cultos espontâneos e fervorosos, muitas vezes sem ordem pré-definida.
Diversidade étnica e social: negros, brancos, latinos, asiáticos, ricos e pobres adoravam juntos — algo radical para os padrões da época.
Ênfase nas manifestações espirituais, como línguas, curas, visões e profecias.
Igualdade de gênero e raça no ministério, com mulheres e homens de diversas origens pregando e liderando.
Impacto
O avivamento da Rua Azusa marcou o nascimento e expansão global do pentecostalismo, hoje uma das maiores forças do cristianismo mundial. Missionários saíram de Azusa para várias partes do mundo, levando a mensagem pentecostal. Movimentos como as Assembleias de Deus e Igreja do Evangelho Quadrangular têm raízes nesse avivamento.
Tensão e Interpretação entre Reformistas e Pentecostalistas
Evangelhos e Atos
João Batista profetiza: “Ele vos batizará com o Espírito Santo e com fogo” (Mateus 3:11).
Em Atos 2, no Pentecostes, os discípulos falam em línguas e recebem poder (Atos 1:8; 2:4).
Outros episódios: Atos 10 (Casa de Cornélio) e Atos 19 (Éfeso).
Cartas Paulinas
Paulo não relaciona diretamente o “batismo com o Espírito” ao falar em línguas. Em 1 Coríntios 12:13 ele diz: “Pois em um só Espírito todos nós fomos batizados em um corpo”.
A glossolalia aparece como um dom entre outros, mas não como evidência obrigatória (1 Coríntios 12:30).
Tensão
Pentecostais veem o batismo com o Espírito como uma segunda experiência após a conversão, evidenciada por línguas. Reformados geralmente interpretam que o batismo com o Espírito ocorre na conversão e que línguas não são obrigatórias ou cessaram com os apóstolos.
Reformadores e o Batismo com o Espírito Santo
Martinho Lutero, João Calvino e outros reformadores não falavam em línguas nem davam ênfase a experiências carismáticas.
Cessacionismo: Doutrina comum entre reformados que diz que os dons sobrenaturais (línguas, profecias, curas) cessaram com a era apostólica.
Continuação (posição pentecostal): Os dons continuam hoje.
Filmes / Documentários
“Azusa Street: The Origins of Pentecostalism” (2006) – Documentário com imagens históricas e entrevistas.
“Wesley” (2009) – Biografia de John Wesley, precursor do metodismo e influência indireta no pentecostalismo.
“The Cross and the Switchblade” (1970) – História de David Wilkerson e a conversão de Nicky Cruz; enfatiza a obra do Espírito.
Série “God in America” (PBS) – Episódio sobre o pentecostalismo (não só Azusa, mas seu impacto cultural).
-
 @ 91bea5cd:1df4451c
2025-02-04 17:15:57
@ 91bea5cd:1df4451c
2025-02-04 17:15:57Definição de ULID:
Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível.
Gerar ULID
```sql
CREATE EXTENSION IF NOT EXISTS pgcrypto;
CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\000\000\000\000\000\000'; output TEXT = '';
unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER);
-- 10 entropy bytes ulid = timestamp || gen_random_bytes(10);
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ```
ULID TO UUID
```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF;
v = regexp_split_to_array(ulid, '');
-- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]);
-- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]);
RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE;
CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ```
UUID to ULID
```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ```
Gera 11 Digitos aleatórios: YBKXG0CKTH4
```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto;
-- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT;
-- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars;END; $$ LANGUAGE plpgsql; ```
Exemplo de USO
```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL );
-- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ```
Fontes
- https://github.com/scoville/pgsql-ulid
- https://github.com/geckoboard/pgulid
-
 @ e4950c93:1b99eccd
2025-05-20 11:06:09
@ e4950c93:1b99eccd
2025-05-20 11:06:09Contenu à venir.
-
 @ 0fa80bd3:ea7325de
2025-01-30 04:28:30
@ 0fa80bd3:ea7325de
2025-01-30 04:28:30"Degeneration" or "Вырождение" ![[photo_2025-01-29 23.23.15.jpeg]]
A once-functional object, now eroded by time and human intervention, stripped of its original purpose. Layers of presence accumulate—marks, alterations, traces of intent—until the very essence is obscured. Restoration is paradoxical: to reclaim, one must erase. Yet erasure is an impossibility, for to remove these imprints is to deny the existence of those who shaped them.
The work stands as a meditation on entropy, memory, and the irreversible dialogue between creation and decay.
-
 @ 6be5cc06:5259daf0
2025-01-21 23:17:29
@ 6be5cc06:5259daf0
2025-01-21 23:17:29A seguir, veja como instalar e configurar o Privoxy no Pop!_OS.
1. Instalar o Tor e o Privoxy
Abra o terminal e execute:
bash sudo apt update sudo apt install tor privoxyExplicação:
- Tor: Roteia o tráfego pela rede Tor.
- Privoxy: Proxy avançado que intermedia a conexão entre aplicativos e o Tor.
2. Configurar o Privoxy
Abra o arquivo de configuração do Privoxy:
bash sudo nano /etc/privoxy/configNavegue até a última linha (atalho:
Ctrl+/depoisCtrl+Vpara navegar diretamente até a última linha) e insira:bash forward-socks5 / 127.0.0.1:9050 .Isso faz com que o Privoxy envie todo o tráfego para o Tor através da porta 9050.
Salve (
CTRL+OeEnter) e feche (CTRL+X) o arquivo.
3. Iniciar o Tor e o Privoxy
Agora, inicie e habilite os serviços:
bash sudo systemctl start tor sudo systemctl start privoxy sudo systemctl enable tor sudo systemctl enable privoxyExplicação:
- start: Inicia os serviços.
- enable: Faz com que iniciem automaticamente ao ligar o PC.
4. Configurar o Navegador Firefox
Para usar a rede Tor com o Firefox:
- Abra o Firefox.
- Acesse Configurações → Configurar conexão.
- Selecione Configuração manual de proxy.
- Configure assim:
- Proxy HTTP:
127.0.0.1 - Porta:
8118(porta padrão do Privoxy) - Domínio SOCKS (v5):
127.0.0.1 - Porta:
9050
- Proxy HTTP:
- Marque a opção "Usar este proxy também em HTTPS".
- Clique em OK.
5. Verificar a Conexão com o Tor
Abra o navegador e acesse:
text https://check.torproject.org/Se aparecer a mensagem "Congratulations. This browser is configured to use Tor.", a configuração está correta.
Dicas Extras
- Privoxy pode ser ajustado para bloquear anúncios e rastreadores.
- Outros aplicativos também podem ser configurados para usar o Privoxy.
-
 @ 56f27915:5fee3024
2025-05-20 11:02:41
@ 56f27915:5fee3024
2025-05-20 11:02:41Buchbeschreibung:\ \ Dieses Buch ist ein Appell.
Es richtet sich nicht nur an den Kopf des Lesers, sondern auch an seinen Willen.\ \ Es ist ein Appell an Volk und Leser, die Lenkung der Geschicke direkt selbst in die Hand zu nehmen. Nicht nur: "Was ist?" sondern vor allem: "Was können wir tun?" ist in diesem Buch die große Frage.\ \ Mit dem Blick auf diese Frage wird das Grundgesetz betrachtet und gezeigt, dass es absolut noch nicht der gediegene Glockenguss ist, als der es uns von "oben" immer vorgestellt wurde, sondern dass in ihm auch extrem gegenläufige, bemessen an seinen freiheitlich-demokratischen Idealen sogar als extrem verfassungs-widrig zu bezeichnende Tendenzen wirken, die heute in seine Zerstörung führen.\ \ Vor allem die unselige Übermacht des Parteienwesens und die damit verbundene systemische Entmündigung des Souveräns, des Volkes, ist das Ergebnis dieser verfassungs-widrigen Tendenzen.\ \ Es wird aber auch gezeigt, wo in den Idealen des Grundgesetzes und in den Entscheidungen der Mütter und Väter dieses Grundgesetzes die Ansatzpunkte liegen, durch die der Zerstörung des Grundgesetzes wirkungsvoll begegnet werden kann. Und diese Ansatzpunkte werden im Buch allseits zur Entfaltung gebracht.\ \ "Wer die Demokratie verteidigen will, der muss sie weiter entwickeln." Im Sinne dieses Wortes wird dem Leser ein praktikabler Weg gewiesen, auf dem er unmittelbar helfen kann, das Grundgesetz den wirkenden Zerstörungskräften zu entwinden, durch Einrichtung der direkten Bürgerbeteiligung an den entscheidenden Fragen unserer Republik die Position des Souveräns gegenüber der Parteienmacht zu stärken, Freiheitsrechte, Demokratie und Rechtsstaat auf eine wesentlich höhere Stufe als bisher zu bringen und sich durch eine verfassungs-klärende Versammlung seine Basis selbst und neu zu geben.
Buch bestellen: https://great-reset-von-unten.de/
\ Und nicht vergessen, abzustimmen! Die Zeit ist reif. Packen wir's an.\
-
 @ cefb08d1:f419beff
2025-05-20 13:26:14
@ cefb08d1:f419beff
2025-05-20 13:26:14https://www.youtube.com/watch?v=jIydjo4B25U
The GWM Catch Up Day 2: Western Australia pushes CT to the ultimate test in all or nothing bouts:
https://www.youtube.com/watch?v=4zwuqs6iTPg
Women and Men Results:
https://stacker.news/items/984538
-
 @ b17fccdf:b7211155
2025-01-21 17:02:21
@ b17fccdf:b7211155
2025-01-21 17:02:21The past 26 August, Tor introduced officially a proof-of-work (PoW) defense for onion services designed to prioritize verified network traffic as a deterrent against denial of service (DoS) attacks.
~ > This feature at the moment, is deactivate by default, so you need to follow these steps to activate this on a MiniBolt node:
- Make sure you have the latest version of Tor installed, at the time of writing this post, which is v0.4.8.6. Check your current version by typing
tor --versionExample of expected output:
Tor version 0.4.8.6. This build of Tor is covered by the GNU General Public License (https://www.gnu.org/licenses/gpl-3.0.en.html) Tor is running on Linux with Libevent 2.1.12-stable, OpenSSL 3.0.9, Zlib 1.2.13, Liblzma 5.4.1, Libzstd N/A and Glibc 2.36 as libc. Tor compiled with GCC version 12.2.0~ > If you have v0.4.8.X, you are OK, if not, type
sudo apt update && sudo apt upgradeand confirm to update.- Basic PoW support can be checked by running this command:
tor --list-modulesExpected output:
relay: yes dirauth: yes dircache: yes pow: **yes**~ > If you have
pow: yes, you are OK- Now go to the torrc file of your MiniBolt and add the parameter to enable PoW for each hidden service added
sudo nano /etc/tor/torrcExample:
```
Hidden Service BTC RPC Explorer
HiddenServiceDir /var/lib/tor/hidden_service_btcrpcexplorer/ HiddenServiceVersion 3 HiddenServicePoWDefensesEnabled 1 HiddenServicePort 80 127.0.0.1:3002 ```
~ > Bitcoin Core and LND use the Tor control port to automatically create the hidden service, requiring no action from the user. We have submitted a feature request in the official GitHub repositories to explore the need for the integration of Tor's PoW defense into the automatic creation process of the hidden service. You can follow them at the following links:
- Bitcoin Core: https://github.com/lightningnetwork/lnd/issues/8002
- LND: https://github.com/bitcoin/bitcoin/issues/28499
More info:
- https://blog.torproject.org/introducing-proof-of-work-defense-for-onion-services/
- https://gitlab.torproject.org/tpo/onion-services/onion-support/-/wikis/Documentation/PoW-FAQ
Enjoy it MiniBolter! 💙
-
 @ cae03c48:2a7d6671
2025-05-20 11:00:00
@ cae03c48:2a7d6671
2025-05-20 11:00:00Bitcoin Magazine

Ben Allen Receives Maelstrom Bitcoin Developer Grant to Advance Payjoin TechBen Allen has been named the third recipient of the Maelstrom Bitcoin Developer Grant, the family office of Arthur Hayes announced in a recent press release sent to Bitcoin Magazine. Over the next year, Allen will focus on enhancing the Payjoin Dev Kit project, a privacy-focused Bitcoin transaction tool designed to improve user anonymity and network scalability.
Payjoin, first introduced in 2019 by Nicolas Dorier in BIP 78, allows both the sender and receiver to contribute inputs to a single Bitcoin transaction. This disrupts common assumptions used by financial surveillance firms, namely the idea that multiple transaction inputs must come from a single entity. By breaking this assumption, even limited adoption of Payjoin can bolster privacy across the Bitcoin network.
“Maelstrom would like to congratulate Ben Allen on this grant,” said Arthur Hayes, Chief Investment Officer of Maelstrom. “The great thing about Payjoin, is that if only a small amount of adoption is achieved, it breaks a key assumption used by financial surveillance companies. The assumption they have is that if a Bitcoin transaction has multiple inputs, all the inputs must all belong to the same entity. Therefore, Payjoin adoption improves the privacy of even the people who don’t use it. We are excited to support Ben Allen’s work on open-source tools and software to increase Payjoin adoption.”
Allen, who will be working alongside Dan Gould, aims to expand the implementation of Payjoin so it can be integrated into more Bitcoin wallets. He acknowledged the technical complexities of the project—including the requirement for receivers to be online—but expressed optimism about overcoming these challenges.
“I’m deeply grateful to Arthur Hayes and Maelstrom for generously providing me with this grant to support my work on the Payjoin Dev Kit project,” said Allen. “With this funding, I can dedicate myself full-time to enhancing the Payjoin implementation, improving testing, and ensuring that the dev kit remains robust, well-documented, and maintainable for the future.”
Allen also emphasized the broader mission of his work: “Improving privacy for bitcoin is an area where continued improvement allows for a better experience by empowering users to control their financial data and foster greater peace of mind when using bitcoin day to day. This is an exciting opportunity to contribute to Bitcoin’s privacy and scalability, and I’m looking forward to continuing to collaborate with the community to make Payjoin more widely adopted.”
Maelstrom, which is focused on supporting digital asset infrastructure, is led by Arthur Hayes, co-founder of BitMEX. Through grants like this one, the firm is investing in the foundational tools that promote a more private, scalable, and decentralized Bitcoin ecosystem.
This post Ben Allen Receives Maelstrom Bitcoin Developer Grant to Advance Payjoin Tech first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ f85b9c2c:d190bcff
2025-05-20 12:51:06
@ f85b9c2c:d190bcff
2025-05-20 12:51:06 Sometimes I feel like reversing time.
I miss my childhood. Honestly, who wouldn’t? Back then, life was so simple, so carefree. I had no bills to pay, no deadlines to chase, and no worries about what tomorrow might bring. All I had to do was wake up, play, eat, and maybe dodge a beating or two from Mum when I got a little too adventurous😂. Sometimes I feel like reversing time, just to relive those golden days when my biggest problem was figuring out how to sneak a piece of meat from the pot without getting caught.
Sometimes I feel like reversing time.
I miss my childhood. Honestly, who wouldn’t? Back then, life was so simple, so carefree. I had no bills to pay, no deadlines to chase, and no worries about what tomorrow might bring. All I had to do was wake up, play, eat, and maybe dodge a beating or two from Mum when I got a little too adventurous😂. Sometimes I feel like reversing time, just to relive those golden days when my biggest problem was figuring out how to sneak a piece of meat from the pot without getting caught.I remember those moments vividly. When I was little, I’d tiptoe into the kitchen, the aroma of Mum’s stew pulling me like a magnet. I’d wait for her to turn her back, then—bam!—my tiny hand would dive into the pot, snagging a juicy piece of meat. Of course, I wasn’t exactly a master thief. Mum always seemed to know. She’d catch me red-handed, and let’s just say her wooden spoon wasn’t just for cooking! I was kinda stubborn back then, so those beatings happened a lot. But I don’t steal meat anymore—grown-up me knows better. Life was different then. My only “job” was to have fun—climbing trees, chasing friends, or making up wild stories in my head. Now, adulthood feels like a never-ending to-do list. I miss the freedom, the laughter, the way problems seemed to vanish with a nap or a hug. If I could, I’d turn back the clock, even just for a day, to feel that lightness again. Childhood wasn’t perfect, but it sure felt like it.
-
 @ 6be5cc06:5259daf0
2025-01-21 01:51:46
@ 6be5cc06:5259daf0
2025-01-21 01:51:46Bitcoin: Um sistema de dinheiro eletrônico direto entre pessoas.
Satoshi Nakamoto
satoshin@gmx.com
www.bitcoin.org
Resumo
O Bitcoin é uma forma de dinheiro digital que permite pagamentos diretos entre pessoas, sem a necessidade de um banco ou instituição financeira. Ele resolve um problema chamado gasto duplo, que ocorre quando alguém tenta gastar o mesmo dinheiro duas vezes. Para evitar isso, o Bitcoin usa uma rede descentralizada onde todos trabalham juntos para verificar e registrar as transações.
As transações são registradas em um livro público chamado blockchain, protegido por uma técnica chamada Prova de Trabalho. Essa técnica cria uma cadeia de registros que não pode ser alterada sem refazer todo o trabalho já feito. Essa cadeia é mantida pelos computadores que participam da rede, e a mais longa é considerada a verdadeira.
Enquanto a maior parte do poder computacional da rede for controlada por participantes honestos, o sistema continuará funcionando de forma segura. A rede é flexível, permitindo que qualquer pessoa entre ou saia a qualquer momento, sempre confiando na cadeia mais longa como prova do que aconteceu.
1. Introdução
Hoje, quase todos os pagamentos feitos pela internet dependem de bancos ou empresas como processadores de pagamento (cartões de crédito, por exemplo) para funcionar. Embora esse sistema seja útil, ele tem problemas importantes porque é baseado em confiança.
Primeiro, essas empresas podem reverter pagamentos, o que é útil em caso de erros, mas cria custos e incertezas. Isso faz com que pequenas transações, como pagar centavos por um serviço, se tornem inviáveis. Além disso, os comerciantes são obrigados a desconfiar dos clientes, pedindo informações extras e aceitando fraudes como algo inevitável.
Esses problemas não existem no dinheiro físico, como o papel-moeda, onde o pagamento é final e direto entre as partes. No entanto, não temos como enviar dinheiro físico pela internet sem depender de um intermediário confiável.
O que precisamos é de um sistema de pagamento eletrônico baseado em provas matemáticas, não em confiança. Esse sistema permitiria que qualquer pessoa enviasse dinheiro diretamente para outra, sem depender de bancos ou processadores de pagamento. Além disso, as transações seriam irreversíveis, protegendo vendedores contra fraudes, mas mantendo a possibilidade de soluções para disputas legítimas.
Neste documento, apresentamos o Bitcoin, que resolve o problema do gasto duplo usando uma rede descentralizada. Essa rede cria um registro público e protegido por cálculos matemáticos, que garante a ordem das transações. Enquanto a maior parte da rede for controlada por pessoas honestas, o sistema será seguro contra ataques.
2. Transações
Para entender como funciona o Bitcoin, é importante saber como as transações são realizadas. Imagine que você quer transferir uma "moeda digital" para outra pessoa. No sistema do Bitcoin, essa "moeda" é representada por uma sequência de registros que mostram quem é o atual dono. Para transferi-la, você adiciona um novo registro comprovando que agora ela pertence ao próximo dono. Esse registro é protegido por um tipo especial de assinatura digital.
O que é uma assinatura digital?
Uma assinatura digital é como uma senha secreta, mas muito mais segura. No Bitcoin, cada usuário tem duas chaves: uma "chave privada", que é secreta e serve para criar a assinatura, e uma "chave pública", que pode ser compartilhada com todos e é usada para verificar se a assinatura é válida. Quando você transfere uma moeda, usa sua chave privada para assinar a transação, provando que você é o dono. A próxima pessoa pode usar sua chave pública para confirmar isso.
Como funciona na prática?
Cada "moeda" no Bitcoin é, na verdade, uma cadeia de assinaturas digitais. Vamos imaginar o seguinte cenário:
- A moeda está com o Dono 0 (você). Para transferi-la ao Dono 1, você assina digitalmente a transação com sua chave privada. Essa assinatura inclui o código da transação anterior (chamado de "hash") e a chave pública do Dono 1.
- Quando o Dono 1 quiser transferir a moeda ao Dono 2, ele assinará a transação seguinte com sua própria chave privada, incluindo também o hash da transação anterior e a chave pública do Dono 2.
- Esse processo continua, formando uma "cadeia" de transações. Qualquer pessoa pode verificar essa cadeia para confirmar quem é o atual dono da moeda.
Resolvendo o problema do gasto duplo
Um grande desafio com moedas digitais é o "gasto duplo", que é quando uma mesma moeda é usada em mais de uma transação. Para evitar isso, muitos sistemas antigos dependiam de uma entidade central confiável, como uma casa da moeda, que verificava todas as transações. No entanto, isso criava um ponto único de falha e centralizava o controle do dinheiro.
O Bitcoin resolve esse problema de forma inovadora: ele usa uma rede descentralizada onde todos os participantes (os "nós") têm acesso a um registro completo de todas as transações. Cada nó verifica se as transações são válidas e se a moeda não foi gasta duas vezes. Quando a maioria dos nós concorda com a validade de uma transação, ela é registrada permanentemente na blockchain.
Por que isso é importante?
Essa solução elimina a necessidade de confiar em uma única entidade para gerenciar o dinheiro, permitindo que qualquer pessoa no mundo use o Bitcoin sem precisar de permissão de terceiros. Além disso, ela garante que o sistema seja seguro e resistente a fraudes.
3. Servidor Timestamp
Para assegurar que as transações sejam realizadas de forma segura e transparente, o sistema Bitcoin utiliza algo chamado de "servidor de registro de tempo" (timestamp). Esse servidor funciona como um registro público que organiza as transações em uma ordem específica.
Ele faz isso agrupando várias transações em blocos e criando um código único chamado "hash". Esse hash é como uma impressão digital que representa todo o conteúdo do bloco. O hash de cada bloco é amplamente divulgado, como se fosse publicado em um jornal ou em um fórum público.
Esse processo garante que cada bloco de transações tenha um registro de quando foi criado e que ele existia naquele momento. Além disso, cada novo bloco criado contém o hash do bloco anterior, formando uma cadeia contínua de blocos conectados — conhecida como blockchain.
Com isso, se alguém tentar alterar qualquer informação em um bloco anterior, o hash desse bloco mudará e não corresponderá ao hash armazenado no bloco seguinte. Essa característica torna a cadeia muito segura, pois qualquer tentativa de fraude seria imediatamente detectada.
O sistema de timestamps é essencial para provar a ordem cronológica das transações e garantir que cada uma delas seja única e autêntica. Dessa forma, ele reforça a segurança e a confiança na rede Bitcoin.
4. Prova-de-Trabalho
Para implementar o registro de tempo distribuído no sistema Bitcoin, utilizamos um mecanismo chamado prova-de-trabalho. Esse sistema é semelhante ao Hashcash, desenvolvido por Adam Back, e baseia-se na criação de um código único, o "hash", por meio de um processo computacionalmente exigente.
A prova-de-trabalho envolve encontrar um valor especial que, quando processado junto com as informações do bloco, gere um hash que comece com uma quantidade específica de zeros. Esse valor especial é chamado de "nonce". Encontrar o nonce correto exige um esforço significativo do computador, porque envolve tentativas repetidas até que a condição seja satisfeita.
Esse processo é importante porque torna extremamente difícil alterar qualquer informação registrada em um bloco. Se alguém tentar mudar algo em um bloco, seria necessário refazer o trabalho de computação não apenas para aquele bloco, mas também para todos os blocos que vêm depois dele. Isso garante a segurança e a imutabilidade da blockchain.
A prova-de-trabalho também resolve o problema de decidir qual cadeia de blocos é a válida quando há múltiplas cadeias competindo. A decisão é feita pela cadeia mais longa, pois ela representa o maior esforço computacional já realizado. Isso impede que qualquer indivíduo ou grupo controle a rede, desde que a maioria do poder de processamento seja mantida por participantes honestos.
Para garantir que o sistema permaneça eficiente e equilibrado, a dificuldade da prova-de-trabalho é ajustada automaticamente ao longo do tempo. Se novos blocos estiverem sendo gerados rapidamente, a dificuldade aumenta; se estiverem sendo gerados muito lentamente, a dificuldade diminui. Esse ajuste assegura que novos blocos sejam criados aproximadamente a cada 10 minutos, mantendo o sistema estável e funcional.
5. Rede
A rede Bitcoin é o coração do sistema e funciona de maneira distribuída, conectando vários participantes (ou nós) para garantir o registro e a validação das transações. Os passos para operar essa rede são:
-
Transmissão de Transações: Quando alguém realiza uma nova transação, ela é enviada para todos os nós da rede. Isso é feito para garantir que todos estejam cientes da operação e possam validá-la.
-
Coleta de Transações em Blocos: Cada nó agrupa as novas transações recebidas em um "bloco". Este bloco será preparado para ser adicionado à cadeia de blocos (a blockchain).
-
Prova-de-Trabalho: Os nós competem para resolver a prova-de-trabalho do bloco, utilizando poder computacional para encontrar um hash válido. Esse processo é como resolver um quebra-cabeça matemático difícil.
-
Envio do Bloco Resolvido: Quando um nó encontra a solução para o bloco (a prova-de-trabalho), ele compartilha esse bloco com todos os outros nós na rede.
-
Validação do Bloco: Cada nó verifica o bloco recebido para garantir que todas as transações nele contidas sejam válidas e que nenhuma moeda tenha sido gasta duas vezes. Apenas blocos válidos são aceitos.
-
Construção do Próximo Bloco: Os nós que aceitaram o bloco começam a trabalhar na criação do próximo bloco, utilizando o hash do bloco aceito como base (hash anterior). Isso mantém a continuidade da cadeia.
Resolução de Conflitos e Escolha da Cadeia Mais Longa
Os nós sempre priorizam a cadeia mais longa, pois ela representa o maior esforço computacional já realizado, garantindo maior segurança. Se dois blocos diferentes forem compartilhados simultaneamente, os nós trabalharão no primeiro bloco recebido, mas guardarão o outro como uma alternativa. Caso o segundo bloco eventualmente forme uma cadeia mais longa (ou seja, tenha mais blocos subsequentes), os nós mudarão para essa nova cadeia.
Tolerância a Falhas
A rede é robusta e pode lidar com mensagens que não chegam a todos os nós. Uma transação não precisa alcançar todos os nós de imediato; basta que chegue a um número suficiente deles para ser incluída em um bloco. Da mesma forma, se um nó não receber um bloco em tempo hábil, ele pode solicitá-lo ao perceber que está faltando quando o próximo bloco é recebido.
Esse mecanismo descentralizado permite que a rede Bitcoin funcione de maneira segura, confiável e resiliente, sem depender de uma autoridade central.
6. Incentivo
O incentivo é um dos pilares fundamentais que sustenta o funcionamento da rede Bitcoin, garantindo que os participantes (nós) continuem operando de forma honesta e contribuindo com recursos computacionais. Ele é estruturado em duas partes principais: a recompensa por mineração e as taxas de transação.
Recompensa por Mineração
Por convenção, o primeiro registro em cada bloco é uma transação especial que cria novas moedas e as atribui ao criador do bloco. Essa recompensa incentiva os mineradores a dedicarem poder computacional para apoiar a rede. Como não há uma autoridade central para emitir moedas, essa é a maneira pela qual novas moedas entram em circulação. Esse processo pode ser comparado ao trabalho de garimpeiros, que utilizam recursos para colocar mais ouro em circulação. No caso do Bitcoin, o "recurso" consiste no tempo de CPU e na energia elétrica consumida para resolver a prova-de-trabalho.
Taxas de Transação
Além da recompensa por mineração, os mineradores também podem ser incentivados pelas taxas de transação. Se uma transação utiliza menos valor de saída do que o valor de entrada, a diferença é tratada como uma taxa, que é adicionada à recompensa do bloco contendo essa transação. Com o passar do tempo e à medida que o número de moedas em circulação atinge o limite predeterminado, essas taxas de transação se tornam a principal fonte de incentivo, substituindo gradualmente a emissão de novas moedas. Isso permite que o sistema opere sem inflação, uma vez que o número total de moedas permanece fixo.
Incentivo à Honestidade
O design do incentivo também busca garantir que os participantes da rede mantenham um comportamento honesto. Para um atacante que consiga reunir mais poder computacional do que o restante da rede, ele enfrentaria duas escolhas:
- Usar esse poder para fraudar o sistema, como reverter transações e roubar pagamentos.
- Seguir as regras do sistema, criando novos blocos e recebendo recompensas legítimas.
A lógica econômica favorece a segunda opção, pois um comportamento desonesto prejudicaria a confiança no sistema, diminuindo o valor de todas as moedas, incluindo aquelas que o próprio atacante possui. Jogar dentro das regras não apenas maximiza o retorno financeiro, mas também preserva a validade e a integridade do sistema.
Esse mecanismo garante que os incentivos econômicos estejam alinhados com o objetivo de manter a rede segura, descentralizada e funcional ao longo do tempo.
7. Recuperação do Espaço em Disco
Depois que uma moeda passa a estar protegida por muitos blocos na cadeia, as informações sobre as transações antigas que a geraram podem ser descartadas para economizar espaço em disco. Para que isso seja possível sem comprometer a segurança, as transações são organizadas em uma estrutura chamada "árvore de Merkle". Essa árvore funciona como um resumo das transações: em vez de armazenar todas elas, guarda apenas um "hash raiz", que é como uma assinatura compacta que representa todo o grupo de transações.
Os blocos antigos podem, então, ser simplificados, removendo as partes desnecessárias dessa árvore. Apenas a raiz do hash precisa ser mantida no cabeçalho do bloco, garantindo que a integridade dos dados seja preservada, mesmo que detalhes específicos sejam descartados.
Para exemplificar: imagine que você tenha vários recibos de compra. Em vez de guardar todos os recibos, você cria um documento e lista apenas o valor total de cada um. Mesmo que os recibos originais sejam descartados, ainda é possível verificar a soma com base nos valores armazenados.
Além disso, o espaço ocupado pelos blocos em si é muito pequeno. Cada bloco sem transações ocupa apenas cerca de 80 bytes. Isso significa que, mesmo com blocos sendo gerados a cada 10 minutos, o crescimento anual em espaço necessário é insignificante: apenas 4,2 MB por ano. Com a capacidade de armazenamento dos computadores crescendo a cada ano, esse espaço continuará sendo trivial, garantindo que a rede possa operar de forma eficiente sem problemas de armazenamento, mesmo a longo prazo.
8. Verificação de Pagamento Simplificada
É possível confirmar pagamentos sem a necessidade de operar um nó completo da rede. Para isso, o usuário precisa apenas de uma cópia dos cabeçalhos dos blocos da cadeia mais longa (ou seja, a cadeia com maior esforço de trabalho acumulado). Ele pode verificar a validade de uma transação ao consultar os nós da rede até obter a confirmação de que tem a cadeia mais longa. Para isso, utiliza-se o ramo Merkle, que conecta a transação ao bloco em que ela foi registrada.
Entretanto, o método simplificado possui limitações: ele não pode confirmar uma transação isoladamente, mas sim assegurar que ela ocupa um lugar específico na cadeia mais longa. Dessa forma, se um nó da rede aprova a transação, os blocos subsequentes reforçam essa aceitação.
A verificação simplificada é confiável enquanto a maioria dos nós da rede for honesta. Contudo, ela se torna vulnerável caso a rede seja dominada por um invasor. Nesse cenário, um atacante poderia fabricar transações fraudulentas que enganariam o usuário temporariamente até que o invasor obtivesse controle completo da rede.
Uma estratégia para mitigar esse risco é configurar alertas nos softwares de nós completos. Esses alertas identificam blocos inválidos, sugerindo ao usuário baixar o bloco completo para confirmar qualquer inconsistência. Para maior segurança, empresas que realizam pagamentos frequentes podem preferir operar seus próprios nós, reduzindo riscos e permitindo uma verificação mais direta e confiável.
9. Combinando e Dividindo Valor
No sistema Bitcoin, cada unidade de valor é tratada como uma "moeda" individual, mas gerenciar cada centavo como uma transação separada seria impraticável. Para resolver isso, o Bitcoin permite que valores sejam combinados ou divididos em transações, facilitando pagamentos de qualquer valor.
Entradas e Saídas
Cada transação no Bitcoin é composta por:
- Entradas: Representam os valores recebidos em transações anteriores.
- Saídas: Correspondem aos valores enviados, divididos entre os destinatários e, eventualmente, o troco para o remetente.
Normalmente, uma transação contém:
- Uma única entrada com valor suficiente para cobrir o pagamento.
- Ou várias entradas combinadas para atingir o valor necessário.
O valor total das saídas nunca excede o das entradas, e a diferença (se houver) pode ser retornada ao remetente como troco.
Exemplo Prático
Imagine que você tem duas entradas:
- 0,03 BTC
- 0,07 BTC
Se deseja enviar 0,08 BTC para alguém, a transação terá:
- Entrada: As duas entradas combinadas (0,03 + 0,07 BTC = 0,10 BTC).
- Saídas: Uma para o destinatário (0,08 BTC) e outra como troco para você (0,02 BTC).
Essa flexibilidade permite que o sistema funcione sem precisar manipular cada unidade mínima individualmente.
Difusão e Simplificação
A difusão de transações, onde uma depende de várias anteriores e assim por diante, não representa um problema. Não é necessário armazenar ou verificar o histórico completo de uma transação para utilizá-la, já que o registro na blockchain garante sua integridade.
10. Privacidade
O modelo bancário tradicional oferece um certo nível de privacidade, limitando o acesso às informações financeiras apenas às partes envolvidas e a um terceiro confiável (como bancos ou instituições financeiras). No entanto, o Bitcoin opera de forma diferente, pois todas as transações são publicamente registradas na blockchain. Apesar disso, a privacidade pode ser mantida utilizando chaves públicas anônimas, que desvinculam diretamente as transações das identidades das partes envolvidas.
Fluxo de Informação
- No modelo tradicional, as transações passam por um terceiro confiável que conhece tanto o remetente quanto o destinatário.
- No Bitcoin, as transações são anunciadas publicamente, mas sem revelar diretamente as identidades das partes. Isso é comparável a dados divulgados por bolsas de valores, onde informações como o tempo e o tamanho das negociações (a "fita") são públicas, mas as identidades das partes não.
Protegendo a Privacidade
Para aumentar a privacidade no Bitcoin, são adotadas as seguintes práticas:
- Chaves Públicas Anônimas: Cada transação utiliza um par de chaves diferentes, dificultando a associação com um proprietário único.
- Prevenção de Ligação: Ao usar chaves novas para cada transação, reduz-se a possibilidade de links evidentes entre múltiplas transações realizadas pelo mesmo usuário.
Riscos de Ligação
Embora a privacidade seja fortalecida, alguns riscos permanecem:
- Transações multi-entrada podem revelar que todas as entradas pertencem ao mesmo proprietário, caso sejam necessárias para somar o valor total.
- O proprietário da chave pode ser identificado indiretamente por transações anteriores que estejam conectadas.
11. Cálculos
Imagine que temos um sistema onde as pessoas (ou computadores) competem para adicionar informações novas (blocos) a um grande registro público (a cadeia de blocos ou blockchain). Este registro é como um livro contábil compartilhado, onde todos podem verificar o que está escrito.
Agora, vamos pensar em um cenário: um atacante quer enganar o sistema. Ele quer mudar informações já registradas para beneficiar a si mesmo, por exemplo, desfazendo um pagamento que já fez. Para isso, ele precisa criar uma versão alternativa do livro contábil (a cadeia de blocos dele) e convencer todos os outros participantes de que essa versão é a verdadeira.
Mas isso é extremamente difícil.
Como o Ataque Funciona
Quando um novo bloco é adicionado à cadeia, ele depende de cálculos complexos que levam tempo e esforço. Esses cálculos são como um grande quebra-cabeça que precisa ser resolvido.
- Os “bons jogadores” (nós honestos) estão sempre trabalhando juntos para resolver esses quebra-cabeças e adicionar novos blocos à cadeia verdadeira.
- O atacante, por outro lado, precisa resolver quebra-cabeças sozinho, tentando “alcançar” a cadeia honesta para que sua versão alternativa pareça válida.
Se a cadeia honesta já está vários blocos à frente, o atacante começa em desvantagem, e o sistema está projetado para que a dificuldade de alcançá-los aumente rapidamente.
A Corrida Entre Cadeias
Você pode imaginar isso como uma corrida. A cada bloco novo que os jogadores honestos adicionam à cadeia verdadeira, eles se distanciam mais do atacante. Para vencer, o atacante teria que resolver os quebra-cabeças mais rápido que todos os outros jogadores honestos juntos.
Suponha que:
- A rede honesta tem 80% do poder computacional (ou seja, resolve 8 de cada 10 quebra-cabeças).
- O atacante tem 20% do poder computacional (ou seja, resolve 2 de cada 10 quebra-cabeças).
Cada vez que a rede honesta adiciona um bloco, o atacante tem que "correr atrás" e resolver mais quebra-cabeças para alcançar.
Por Que o Ataque Fica Cada Vez Mais Improvável?
Vamos usar uma fórmula simples para mostrar como as chances de sucesso do atacante diminuem conforme ele precisa "alcançar" mais blocos:
P = (q/p)^z
- q é o poder computacional do atacante (20%, ou 0,2).
- p é o poder computacional da rede honesta (80%, ou 0,8).
- z é a diferença de blocos entre a cadeia honesta e a cadeia do atacante.
Se o atacante está 5 blocos atrás (z = 5):
P = (0,2 / 0,8)^5 = (0,25)^5 = 0,00098, (ou, 0,098%)
Isso significa que o atacante tem menos de 0,1% de chance de sucesso — ou seja, é muito improvável.
Se ele estiver 10 blocos atrás (z = 10):
P = (0,2 / 0,8)^10 = (0,25)^10 = 0,000000095, (ou, 0,0000095%).
Neste caso, as chances de sucesso são praticamente nulas.
Um Exemplo Simples
Se você jogar uma moeda, a chance de cair “cara” é de 50%. Mas se precisar de 10 caras seguidas, sua chance já é bem menor. Se precisar de 20 caras seguidas, é quase impossível.
No caso do Bitcoin, o atacante precisa de muito mais do que 20 caras seguidas. Ele precisa resolver quebra-cabeças extremamente difíceis e alcançar os jogadores honestos que estão sempre à frente. Isso faz com que o ataque seja inviável na prática.
Por Que Tudo Isso é Seguro?
- A probabilidade de sucesso do atacante diminui exponencialmente. Isso significa que, quanto mais tempo passa, menor é a chance de ele conseguir enganar o sistema.
- A cadeia verdadeira (honesta) está protegida pela força da rede. Cada novo bloco que os jogadores honestos adicionam à cadeia torna mais difícil para o atacante alcançar.
E Se o Atacante Tentar Continuar?
O atacante poderia continuar tentando indefinidamente, mas ele estaria gastando muito tempo e energia sem conseguir nada. Enquanto isso, os jogadores honestos estão sempre adicionando novos blocos, tornando o trabalho do atacante ainda mais inútil.
Assim, o sistema garante que a cadeia verdadeira seja extremamente segura e que ataques sejam, na prática, impossíveis de ter sucesso.
12. Conclusão
Propusemos um sistema de transações eletrônicas que elimina a necessidade de confiança, baseando-se em assinaturas digitais e em uma rede peer-to-peer que utiliza prova de trabalho. Isso resolve o problema do gasto duplo, criando um histórico público de transações imutável, desde que a maioria do poder computacional permaneça sob controle dos participantes honestos. A rede funciona de forma simples e descentralizada, com nós independentes que não precisam de identificação ou coordenação direta. Eles entram e saem livremente, aceitando a cadeia de prova de trabalho como registro do que ocorreu durante sua ausência. As decisões são tomadas por meio do poder de CPU, validando blocos legítimos, estendendo a cadeia e rejeitando os inválidos. Com este mecanismo de consenso, todas as regras e incentivos necessários para o funcionamento seguro e eficiente do sistema são garantidos.
Faça o download do whitepaper original em português: https://bitcoin.org/files/bitcoin-paper/bitcoin_pt_br.pdf
-
 @ cae03c48:2a7d6671
2025-05-20 10:50:37
@ cae03c48:2a7d6671
2025-05-20 10:50:37Bitcoin Magazine
Proof of Reserves Should Be the Standard for Bitcoin Treasury Companies“The root problem with conventional currency is all the trust that’s required to make it work. The central bank must be trusted not to debase the currency, but the history of fiat currencies is full of breaches of that trust. Banks must be trusted to hold our money and transfer it electronically, but they lend it out in waves of credit bubbles with barely a fraction in reserve.”
— Satoshi Nakamoto (2009)
Bitcoin was created to eliminate the need for trusted intermediaries. It replaced opaque, permissioned systems with transparency, auditability, and decentralized verification. The ethos was clear from day one: don’t trust—verify.
And yet, many of the institutions now holding Bitcoin—custodians, exchanges, ETFs, even public companies—continue to rely on trust-based assumptions, the very problem Bitcoin was designed to solve.
For Bitcoin treasury companies, this contradiction is especially glaring. These are firms that claim to operate on a Bitcoin standard—yet without verifiable Proof of Reserves (PoR), there’s no way for shareholders to know whether the Bitcoin is actually there.
The Problem: Unproven Bitcoin Is Just Another IOU
Bitcoin is designed to be verifiable—but most corporate disclosures aren’t. When companies report BTC holdings without public wallet visibility or on-chain proof, investors are left to trust balance sheets, auditors, and custodians.
That opens the door to systemic risks:
- Rehypothecation: BTC pledged or lent behind the scenes
- Custodial failure: Centralized services operating without 1:1 backing
- “Paper Bitcoin”: Multiple claims on the same BTC, echoing legacy financial opacity
The mere presence of Bitcoin on a balance sheet is not a guarantee. Without verification, it’s no different than a fiat-denominated claim—an IOU dressed up in BTC terms.
What We Learned from Gold: The Paper Problem
Bitcoin is not the first hard asset to face this challenge. The gold market offers a cautionary tale.
For decades, gold investors have dealt with “paper gold” systems—unallocated accounts, synthetic ETFs, and derivatives with little or no linkage to actual metal. These claims often outnumber real reserves many times over, leading to widespread suspicion of price distortion and systemic misrepresentation.
Most gold investors don’t own gold—they own a claim to gold. And they have no way to prove it.
Bitcoin gives us the tools to break this cycle. But only if companies choose to use them.
Bitcoin Is Built for Proof—and Companies Should Use It
Unlike legacy assets, Bitcoin is designed to make proof of ownership and solvency a native function of the asset itself. Through public key cryptography, on-chain auditability, and permissionless transparency, Bitcoin enables real-time, trust-minimized verification.
This isn’t just a technical capability—it’s a governance feature. Bitcoin allows companies to demonstrate, cryptographically and without intermediaries, that their reserves exist, are intact, and are unencumbered. No bank statements. No opaque custodial claims. Just data, on-chain.
That’s a radical shift—and it’s one that Bitcoin treasury companies are uniquely positioned to take advantage of. In doing so, they can reduce audit complexity, strengthen shareholder communication, and align their internal capital practices with the trustless architecture of the asset they’re holding.
And it’s already happening. Metaplanet, Premiere Member of Bitcoin For Corporations, publicly discloses its BTC reserve addresses and transaction history. Anyone in the world—including shareholders, analysts, and regulators—can independently verify the existence and movement of their treasury. That’s not just compliance. That’s Bitcoin, applied. View the snapshot of Metaplanet’s proof of reserves dashboard below.

Public Companies Face the Greatest Responsibility
Public companies don’t operate in a vacuum. Their disclosures shape market perception, influence investor behavior, and—especially when Bitcoin is involved—serve as a proxy for the maturity of the asset class itself.
When a publicly traded company holds Bitcoin but offers no visibility into how that Bitcoin is held or verified, it exposes itself to multiple levels of risk: legal, reputational, operational, and strategic. It undermines trust at the very moment it claims to be embracing a trustless system.
More importantly, public companies send signals. Whether they like it or not, they become de facto representatives of the Bitcoin strategy they’ve adopted. Their behavior becomes part of the playbook for others considering similar moves.
That’s why the responsibility is higher. Transparency isn’t optional for companies who lead with Bitcoin. It’s a duty. And companies that choose opacity not only take on unnecessary risk—they weaken the credibility of the entire movement.e.
What Proof of Reserves Should Actually Include
For Proof of Reserves to have real integrity, it must go beyond vague references to “custody partners” or internal assurance statements. The key is verifiability—independent, data-driven, and actionable by any shareholder or auditor.
At a minimum, Bitcoin treasury companies should provide:
- Custody model clarity: Is the company using self-custody, shared multisig, or third-party solutions? Who controls the keys, and under what governance?
- On-chain transparency: Whether through view-only wallet addresses or cryptographic attestations (like Merkle tree proofs), companies must make it possible to verify balances against public disclosures.
- Encumbrance disclosure: Reserves that are pledged, lent out, or locked in yield strategies should be disclosed clearly, with timelines and risk parameters attached.
- Routine updates: Proof should be refreshed regularly—not once per year in an audit footnote, but as part of ongoing financial communication.
- Reconciliation framework: Companies should explain how on-chain data maps to reported BTC NAV in filings or investor materials.
For boards and CFOs, this doesn’t need to introduce operational risk. Tools already exist—xpub view-only wallets, custody APIs, third-party validators—to provide assurance without compromising security. The obstacle isn’t capability. It’s willingness.
Setting the Industry Benchmark: Where Bitcoin Treasury Companies Must Lead
Bitcoin treasury companies are not just financial outliers—they are structural pioneers. Their decision to hold BTC signals not only a belief in long-term value, but a rejection of legacy capital inefficiency. That’s why they must also lead on standards of integrity.
By adopting PoR voluntarily and early, companies can position themselves as trustworthy, sophisticated, and future-ready. This will matter more as institutional capital rotates into Bitcoin, as index inclusion expands, and as regulators begin asking sharper questions about crypto asset disclosures on balance sheets.
PoR isn’t just a way to comply with future standards—it’s a way to shape them. The companies that lead now will not only avoid future scrutiny—they’ll attract capital from allocators who are seeking transparency but don’t yet know where to find it.
At BFC, we believe the market rewards clarity. Bitcoin treasury companies have a chance to bake transparency into their structure, not as an afterthought, but as a strategic differentiator.
Shareholders Must Demand It
Proof of Reserves isn’t just a company initiative—it’s a shareholder obligation. When a public company holds Bitcoin on its balance sheet, it is acting as a fiduciary for shareholder capital denominated in one of the hardest, most transparent assets in history. To accept opacity in that context is to forfeit the very advantage Bitcoin offers.
If you’re an investor in a Bitcoin treasury company and you can’t verify the Bitcoin, you don’t own a monetary reserve—you own a narrative. You’re trusting that someone else is telling the truth, rather than requiring the proof Bitcoin makes possible.
That’s not aligned with the principles of sound capital stewardship.
Institutional allocators, activist shareholders, and governance professionals have a growing role to play here. Just as proxy advisors and investor coalitions have pushed for climate disclosures, board transparency, and ESG clarity in the past decade, it’s time to apply that same rigor to Bitcoin disclosures—especially for companies who claim to operate on a Bitcoin standard.
Demand direct answers:
- Can we verify the holdings on-chain?
- Are reserves fully collateralized and unencumbered?
- Has manageme
-
 @ 3f770d65:7a745b24
2025-01-19 21:48:49
@ 3f770d65:7a745b24
2025-01-19 21:48:49The recent shutdown of TikTok in the United States due to a potential government ban serves as a stark reminder how fragile centralized platforms truly are under the surface. While these platforms offer convenience, a more polished user experience, and connectivity, they are ultimately beholden to governments, corporations, and other authorities. This makes them vulnerable to censorship, regulation, and outright bans. In contrast, Nostr represents a shift in how we approach online communication and content sharing. Built on the principles of decentralization and user choice, Nostr cannot be banned, because it is not a platform—it is a protocol.
PROTOCOLS, NOT PLATFORMS.
At the heart of Nostr's philosophy is user choice, a feature that fundamentally sets it apart from legacy platforms. In centralized systems, the user experience is dictated by a single person or governing entity. If the platform decides to filter, censor, or ban specific users or content, individuals are left with little action to rectify the situation. They must either accept the changes or abandon the platform entirely, often at the cost of losing their social connections, their data, and their identity.
What's happening with TikTok could never happen on Nostr. With Nostr, the dynamics are completely different. Because it is a protocol, not a platform, no single entity controls the ecosystem. Instead, the protocol enables a network of applications and relays that users can freely choose from. If a particular application or relay implements policies that a user disagrees with, such as censorship, filtering, or even government enforced banning, they are not trapped or abandoned. They have the freedom to move to another application or relay with minimal effort.
THIS IS POWERFUL.
Take, for example, the case of a relay that decides to censor specific content. On a legacy platform, this would result in frustration and a loss of access for users. On Nostr, however, users can simply connect to a different relay that does not impose such restrictions. Similarly, if an application introduces features or policies that users dislike, they can migrate to a different application that better suits their preferences, all while retaining their identity and social connections.
The same principles apply to government bans and censorship. A government can ban a specific application or even multiple applications, just as it can block one relay or several relays. China has implemented both tactics, yet Chinese users continue to exist and actively participate on Nostr, demonstrating Nostr's ability to resistant censorship.
How? Simply, it turns into a game of whack-a-mole. When one relay is censored, another quickly takes its place. When one application is banned, another emerges. Users can also bypass these obstacles by running their own relays and applications directly from their homes or personal devices, eliminating reliance on larger entities or organizations and ensuring continuous access.
AGAIN, THIS IS POWERUFL.
Nostr's open and decentralized design makes it resistant to the kinds of government intervention that led to TikTok's outages this weekend and potential future ban in the next 90 days. There is no central server to target, no company to regulate, and no single point of failure. (Insert your CEO jokes here). As long as there are individuals running relays and applications, users continue creating notes and sending zaps.
Platforms like TikTok can be silenced with the stroke of a pen, leaving millions of users disconnected and abandoned. Social communication should not be silenced so incredibly easily. No one should have that much power over social interactions.
Will we on-board a massive wave of TikTokers in the coming hours or days? I don't know.
TikTokers may not be ready for Nostr yet, and honestly, Nostr may not be ready for them either. The ecosystem still lacks the completely polished applications, tools, and services they’re accustomed to. This is where we say "we're still early". They may not be early adopters like the current Nostr user base. Until we bridge that gap, they’ll likely move to the next centralized platform, only to face another government ban or round of censorship in the future. But eventually, there will come a tipping point, a moment when they’ve had enough. When that time comes, I hope we’re prepared. If we’re not, we risk missing a tremendous opportunity to onboard people who genuinely need Nostr’s freedom.
Until then, to all of the Nostr developers out there, keep up the great work and keep building. Your hard work and determination is needed.
-
 @ cff1720e:15c7e2b2
2025-01-19 17:48:02
@ cff1720e:15c7e2b2
2025-01-19 17:48:02Einleitung\ \ Schwierige Dinge einfach zu erklären ist der Anspruch von ELI5 (explain me like I'm 5). Das ist in unserer hoch technisierten Welt dringend erforderlich, denn nur mit dem Verständnis der Technologien können wir sie richtig einsetzen und weiter entwickeln.\ Ich starte meine Serie mit Nostr, einem relativ neuen Internet-Protokoll. Was zum Teufel ist ein Internet-Protokoll? Formal beschrieben sind es internationale Standards, die dafür sorgen, dass das Internet seit über 30 Jahren ziemlich gut funktioniert. Es ist die Sprache, in der sich die Rechner miteinander unterhalten und die auch Sie täglich nutzen, vermutlich ohne es bewusst wahrzunehmen. http(s) transportiert ihre Anfrage an einen Server (z.B. Amazon), und html sorgt dafür, dass aus den gelieferten Daten eine schöne Seite auf ihrem Bildschirm entsteht. Eine Mail wird mit smtp an den Mailserver gesendet und mit imap von ihm abgerufen, und da alle den Standard verwenden, funktioniert das mit jeder App auf jedem Betriebssystem und mit jedem Mail-Provider. Und mit einer Mail-Adresse wie roland@pareto.space können sie sogar jederzeit umziehen, egal wohin. Cool, das ist state of the art! Aber warum funktioniert das z.B. bei Chat nicht, gibt es da kein Protokoll? Doch, es heißt IRC (Internet Relay Chat → merken sie sich den Namen), aber es wird so gut wie nicht verwendet. Die Gründe dafür sind nicht technischer Natur, vielmehr wurden mit Apps wie Facebook, Twitter, WhatsApp, Telegram, Instagram, TikTok u.a. bewusst Inkompatibilitäten und Nutzerabhängigkeiten geschaffen um Profite zu maximieren.

Warum Nostr?
Da das Standard-Protokoll nicht genutzt wird, hat jede App ihr eigenes, und wir brauchen eine handvoll Apps um uns mit allen Bekannten auszutauschen. Eine Mobilfunknummer ist Voraussetzung für jedes Konto, damit können die App-Hersteller die Nutzer umfassend tracken und mit dem Verkauf der Informationen bis zu 30 USD je Konto und Monat verdienen. Der Nutzer ist nicht mehr Kunde, er ist das Produkt! Der Werbe-SPAM ist noch das kleinste Problem bei diesem Geschäftsmodell. Server mit Millionen von Nutzerdaten sind ein “honey pot”, dementsprechend oft werden sie gehackt und die Zugangsdaten verkauft. 2024 wurde auch der Twitter-Account vom damaligen Präsidenten Joe Biden gehackt, niemand wusste mehr wer die Nachrichten verfasst hat (vorher auch nicht), d.h. die Authentizität der Inhalte ist bei keinem dieser Anbieter gewährleistet. Im selben Jahr wurde der Telegram-Gründer in Frankreich in Beugehaft genommen, weil er sich geweigert hatte Hintertüren in seine Software einzubauen. Nun kann zum Schutz "unserer Demokratie” praktisch jeder mitlesen, was sie mit wem an Informationen austauschen, z.B. darüber welches Shampoo bestimmte Politiker verwenden.

Und wer tatsächlich glaubt er könne Meinungsfreiheit auf sozialen Medien praktizieren, findet sich schnell in der Situation von Donald Trump wieder (seinerzeit amtierender Präsident), dem sein Twitter-Konto 2021 abgeschaltet wurde (Cancel-Culture). Die Nutzerdaten, also ihr Profil, ihre Kontakte, Dokumente, Bilder, Videos und Audiofiles - gehören ihnen ohnehin nicht mehr sondern sind Eigentum des Plattform-Betreibers; lesen sie sich mal die AGB's durch. Aber nein, keine gute Idee, das sind hunderte Seiten und sie werden permanent geändert. Alle nutzen also Apps, deren Technik sie nicht verstehen, deren Regeln sie nicht kennen, wo sie keine Rechte haben und die ihnen die Resultate ihres Handelns stehlen. Was würde wohl der Fünfjährige sagen, wenn ihm seine ältere Schwester anbieten würde, alle seine Spielzeuge zu “verwalten” und dann auszuhändigen wenn er brav ist? “Du spinnst wohl”, und damit beweist der Knirps mehr Vernunft als die Mehrzahl der Erwachsenen. \ \ Resümee: keine Standards, keine Daten, keine Rechte = keine Zukunft!

\ Wie funktioniert Nostr?
Die Entwickler von Nostr haben erkannt dass sich das Server-Client-Konzept in ein Master-Slave-Konzept verwandelt hatte. Der Master ist ein Synonym für Zentralisierung und wird zum “single point of failure”, der zwangsläufig Systeme dysfunktional macht. In einem verteilten Peer2Peer-System gibt es keine Master mehr sondern nur gleichberechtigte Knoten (Relays), auf denen die Informationen gespeichert werden. Indem man Informationen auf mehreren Relays redundant speichert, ist das System in jeglicher Hinsicht resilienter. Nicht nur die Natur verwendet dieses Prinzip seit Jahrmillionen erfolgreich, auch das Internet wurde so konzipiert (das ARPAnet wurde vom US-Militär für den Einsatz in Kriegsfällen unter massiven Störungen entwickelt). Alle Nostr-Daten liegen auf Relays und der Nutzer kann wählen zwischen öffentlichen (zumeist kostenlosen) und privaten Relays, z.B. für geschlossene Gruppen oder zum Zwecke von Daten-Archivierung. Da Dokumente auf mehreren Relays gespeichert sind, werden statt URL's (Locator) eindeutige Dokumentnamen (URI's = Identifier) verwendet, broken Links sind damit Vergangenheit und Löschungen / Verluste ebenfalls.\ \ Jedes Dokument (Event genannt) wird vom Besitzer signiert, es ist damit authentisch und fälschungssicher und kann nur vom Ersteller gelöscht werden. Dafür wird ein Schlüsselpaar verwendet bestehend aus privatem (nsec) und öffentlichem Schlüssel (npub) wie aus der Mailverschlüsselung (PGP) bekannt. Das repräsentiert eine Nostr-Identität, die um Bild, Namen, Bio und eine lesbare Nostr-Adresse ergänzt werden kann (z.B. roland@pareto.space ), mehr braucht es nicht um alle Ressourcen des Nostr-Ökosystems zu nutzen. Und das besteht inzwischen aus über hundert Apps mit unterschiedlichen Fokussierungen, z.B. für persönliche verschlüsselte Nachrichten (DM → OxChat), Kurznachrichten (Damus, Primal), Blogbeiträge (Pareto), Meetups (Joinstr), Gruppen (Groups), Bilder (Olas), Videos (Amethyst), Audio-Chat (Nostr Nests), Audio-Streams (Tunestr), Video-Streams (Zap.Stream), Marktplätze (Shopstr) u.v.a.m. Die Anmeldung erfolgt mit einem Klick (single sign on) und den Apps stehen ALLE Nutzerdaten zur Verfügung (Profil, Daten, Kontakte, Social Graph → Follower, Bookmarks, Comments, etc.), im Gegensatz zu den fragmentierten Datensilos der Gegenwart.\ \ Resümee: ein offener Standard, alle Daten, alle Rechte = große Zukunft!

\ Warum ist Nostr die Zukunft des Internet?
“Baue Dein Haus nicht auf einem fremden Grundstück” gilt auch im Internet - für alle App-Entwickler, Künstler, Journalisten und Nutzer, denn auch ihre Daten sind werthaltig. Nostr garantiert das Eigentum an den Daten, und überwindet ihre Fragmentierung. Weder die Nutzung noch die kreativen Freiheiten werden durch maßlose Lizenz- und Nutzungsbedingungen eingeschränkt. Aus passiven Nutzern werden durch Interaktion aktive Teilnehmer, Co-Creatoren in einer Sharing-Ökonomie (Value4Value). OpenSource schafft endlich wieder Vertrauen in die Software und ihre Anbieter. Offene Standards ermöglichen den Entwicklern mehr Kooperation und schnellere Entwicklung, für die Anwender garantieren sie Wahlfreiheit. Womit wir letztmalig zu unserem Fünfjährigen zurückkehren. Kinder lieben Lego über alles, am meisten die Maxi-Box “Classic”, weil sie damit ihre Phantasie im Kombinieren voll ausleben können. Erwachsene schenken ihnen dann die viel zu teuren Themenpakete, mit denen man nur eine Lösung nach Anleitung bauen kann. “Was stimmt nur mit meinen Eltern nicht, wann sind die denn falsch abgebogen?" fragt sich der Nachwuchs zu Recht. Das Image lässt sich aber wieder aufpolieren, wenn sie ihren Kindern Nostr zeigen, denn die Vorteile verstehen sogar Fünfjährige.

\ Das neue Internet ist dezentral. Das neue Internet ist selbstbestimmt. Nostr ist das neue Internet.
https://nostr.net/ \ https://start.njump.me/
Hier das Interview zum Thema mit Radio Berliner Morgenröte
-
 @ 9be6a199:6e133301
2025-05-20 12:47:14
@ 9be6a199:6e133301
2025-05-20 12:47:14sadfsflkjsdflkdsjfglksjdfglksdaasdfsdfsdfsdfssdsd
-
 @ 39cc53c9:27168656
2025-05-20 10:45:31
@ 39cc53c9:27168656
2025-05-20 10:45:31The new website is finally live! I put in a lot of hard work over the past months on it. I'm proud to say that it's out now and it looks pretty cool, at least to me!
Why rewrite it all?
The old kycnot.me site was built using Python with Flask about two years ago. Since then, I've gained a lot more experience with Golang and coding in general. Trying to update that old codebase, which had a lot of design flaws, would have been a bad idea. It would have been like building on an unstable foundation.
That's why I made the decision to rewrite the entire application. Initially, I chose to use SvelteKit with JavaScript. I did manage to create a stable site that looked similar to the new one, but it required Jav aScript to work. As I kept coding, I started feeling like I was repeating "the Python mistake". I was writing the app in a language I wasn't very familiar with (just like when I was learning Python at that mom ent), and I wasn't happy with the code. It felt like spaghetti code all the time.
So, I made a complete U-turn and started over, this time using Golang. While I'm not as proficient in Golang as I am in Python now, I find it to be a very enjoyable language to code with. Most aof my recent pr ojects have been written in Golang, and I'm getting the hang of it. I tried to make the best decisions I could and structure the code as well as possible. Of course, there's still room for improvement, which I'll address in future updates.
Now I have a more maintainable website that can scale much better. It uses a real database instead of a JSON file like the old site, and I can add many more features. Since I chose to go with Golang, I mad e the "tradeoff" of not using JavaScript at all, so all the rendering load falls on the server. But I believe it's a tradeoff that's worth it.
What's new
- UI/UX - I've designed a new logo and color palette for kycnot.me. I think it looks pretty cool and cypherpunk. I am not a graphic designer, but I think I did a decent work and I put a lot of thinking on it to make it pleasant!
- Point system - The new point system provides more detailed information about the listings, and can be expanded to cover additional features across all services. Anyone can request a new point!
- ToS Scrapper: I've implemented a powerful automated terms-of-service scrapper that collects all the ToS pages from the listings. It saves you from the hassle of reading the ToS by listing the lines that are suspiciously related to KYC/AML practices. This is still in development and it will improve for sure, but it works pretty fine right now!
- Search bar - The new search bar allows you to easily filter services. It performs a full-text search on the Title, Description, Category, and Tags of all the services. Looking for VPN services? Just search for "vpn"!
- Transparency - To be more transparent, all discussions about services now take place publicly on GitLab. I won't be answering any e-mails (an auto-reply will prompt to write to the corresponding Gitlab issue). This ensures that all service-related matters are publicly accessible and recorded. Additionally, there's a real-time audits page that displays database changes.
- Listing Requests - I have upgraded the request system. The new form allows you to directly request services or points without any extra steps. In the future, I plan to enable requests for specific changes to parts of the website.
- Lightweight and fast - The new site is lighter and faster than its predecessor!
- Tor and I2P - At last! kycnot.me is now officially on Tor and I2P!
How?
This rewrite has been a labor of love, in the end, I've been working on this for more than 3 months now. I don't have a team, so I work by myself on my free time, but I find great joy in helping people on their private journey with cryptocurrencies. Making it easier for individuals to use cryptocurrencies without KYC is a goal I am proud of!
If you appreciate my work, you can support me through the methods listed here. Alternatively, feel free to send me an email with a kind message!
Technical details
All the code is written in Golang, the website makes use of the chi router for the routing part. I also make use of BigCache for caching database requests. There is 0 JavaScript, so all the rendering load falls on the server, this means it needed to be efficient enough to not drawn with a few users since the old site was reporting about 2M requests per month on average (note that this are not unique users).
The database is running with mariadb, using gorm as the ORM. This is more than enough for this project. I started working with an
sqlitedatabase, but I ended up migrating to mariadb since it works better with JSON.The scraper is using chromedp combined with a series of keywords, regex and other logic. It runs every 24h and scraps all the services. You can find the scraper code here.
The frontend is written using Golang Templates for the HTML, and TailwindCSS plus DaisyUI for the CSS classes framework. I also use some plain CSS, but it's minimal.
The requests forms is the only part of the project that requires JavaScript to be enabled. It is needed for parsing some from fields that are a bit complex and for the "captcha", which is a simple Proof of Work that runs on your browser, destinated to avoid spam. For this, I use mCaptcha.
-
 @ f9cf4e94:96abc355
2025-01-18 06:09:50
@ f9cf4e94:96abc355
2025-01-18 06:09:50Para esse exemplo iremos usar: | Nome | Imagem | Descrição | | --------------- | ------------------------------------------------------------ | ------------------------------------------------------------ | | Raspberry PI B+ |
 | Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |
| Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |  | 16Gb |
| 16Gb |Recomendo que use o Ubuntu Server para essa instalação. Você pode baixar o Ubuntu para Raspberry Pi aqui. O passo a passo para a instalação do Ubuntu no Raspberry Pi está disponível aqui. Não instale um desktop (como xubuntu, lubuntu, xfce, etc.).
Passo 1: Atualizar o Sistema 🖥️
Primeiro, atualize seu sistema e instale o Tor:
bash apt update apt install tor
Passo 2: Criar o Arquivo de Serviço
nrs.service🔧Crie o arquivo de serviço que vai gerenciar o servidor Nostr. Você pode fazer isso com o seguinte conteúdo:
```unit [Unit] Description=Nostr Relay Server Service After=network.target
[Service] Type=simple WorkingDirectory=/opt/nrs ExecStart=/opt/nrs/nrs-arm64 Restart=on-failure
[Install] WantedBy=multi-user.target ```
Passo 3: Baixar o Binário do Nostr 🚀
Baixe o binário mais recente do Nostr aqui no GitHub.
Passo 4: Criar as Pastas Necessárias 📂
Agora, crie as pastas para o aplicativo e o pendrive:
bash mkdir -p /opt/nrs /mnt/edriver
Passo 5: Listar os Dispositivos Conectados 🔌
Para saber qual dispositivo você vai usar, liste todos os dispositivos conectados:
bash lsblk
Passo 6: Formatando o Pendrive 💾
Escolha o pendrive correto (por exemplo,
/dev/sda) e formate-o:bash mkfs.vfat /dev/sda
Passo 7: Montar o Pendrive 💻
Monte o pendrive na pasta
/mnt/edriver:bash mount /dev/sda /mnt/edriver
Passo 8: Verificar UUID dos Dispositivos 📋
Para garantir que o sistema monte o pendrive automaticamente, liste os UUID dos dispositivos conectados:
bash blkid
Passo 9: Alterar o
fstabpara Montar o Pendrive Automáticamente 📝Abra o arquivo
/etc/fstabe adicione uma linha para o pendrive, com o UUID que você obteve no passo anterior. A linha deve ficar assim:fstab UUID=9c9008f8-f852 /mnt/edriver vfat defaults 0 0
Passo 10: Copiar o Binário para a Pasta Correta 📥
Agora, copie o binário baixado para a pasta
/opt/nrs:bash cp nrs-arm64 /opt/nrs
Passo 11: Criar o Arquivo de Configuração 🛠️
Crie o arquivo de configuração com o seguinte conteúdo e salve-o em
/opt/nrs/config.yaml:yaml app_env: production info: name: Nostr Relay Server description: Nostr Relay Server pub_key: "" contact: "" url: http://localhost:3334 icon: https://external-content.duckduckgo.com/iu/?u= https://public.bnbstatic.com/image/cms/crawler/COINCU_NEWS/image-495-1024x569.png base_path: /mnt/edriver negentropy: true
Passo 12: Copiar o Serviço para o Diretório de Systemd ⚙️
Agora, copie o arquivo
nrs.servicepara o diretório/etc/systemd/system/:bash cp nrs.service /etc/systemd/system/Recarregue os serviços e inicie o serviço
nrs:bash systemctl daemon-reload systemctl enable --now nrs.service
Passo 13: Configurar o Tor 🌐
Abra o arquivo de configuração do Tor
/var/lib/tor/torrce adicione a seguinte linha:torrc HiddenServiceDir /var/lib/tor/nostr_server/ HiddenServicePort 80 127.0.0.1:3334
Passo 14: Habilitar e Iniciar o Tor 🧅
Agora, ative e inicie o serviço Tor:
bash systemctl enable --now tor.serviceO Tor irá gerar um endereço
.onionpara o seu servidor Nostr. Você pode encontrá-lo no arquivo/var/lib/tor/nostr_server/hostname.
Observações ⚠️
- Com essa configuração, os dados serão salvos no pendrive, enquanto o binário ficará no cartão SD do Raspberry Pi.
- O endereço
.oniondo seu servidor Nostr será algo como:ws://y3t5t5wgwjif<exemplo>h42zy7ih6iwbyd.onion.
Agora, seu servidor Nostr deve estar configurado e funcionando com Tor! 🥳
Se este artigo e as informações aqui contidas forem úteis para você, convidamos a considerar uma doação ao autor como forma de reconhecimento e incentivo à produção de novos conteúdos.
-
 @ 39cc53c9:27168656
2025-05-20 10:45:29
@ 39cc53c9:27168656
2025-05-20 10:45:29Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations.
Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms.
Rights for Illusions
KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks?
The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors."
However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% ^1 – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service.
Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy.
To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% ^1 of less-than-careful criminals.
KYC? Not you.
KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. ^2
KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible.
For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded.
Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether.
It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms.
You're not welcome
Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right?
This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to.
Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely.
Your identity has been stolen
KYC data has been found to be for sale on many dark net markets^3. Exchanges may have leaks or hacks, and such leaks contain very sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it?
As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. ^3
In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised.
(they) Know Your Coins
You may already know that Bitcoin and most cryptocurrencies have a transparent public blockchain, meaning that all data is shown unencrypted for everyone to see and recorded forever. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced.
If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with.
Conclusions
To sum up, KYC does not protect individuals; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred.
The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies.
The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable.
Edited 20/03/2024 * Add reference to the 1% statement on Rights for Illusions section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity ^1
-
 @ 9be6a199:6e133301
2025-05-20 12:46:43
@ 9be6a199:6e133301
2025-05-20 12:46:43sadfsflkjsdflkdsjfglksjdfglksdaasdfsdfsdfsdfssdsd
-
 @ 39cc53c9:27168656
2025-05-20 10:45:28
@ 39cc53c9:27168656
2025-05-20 10:45:28Over the past few months, I've dedicated my time to a complete rewrite of the kycnot.me website. The technology stack remains unchanged; Golang paired with TailwindCSS. However, I've made some design choices in this iteration that I believe significantly enhance the site. Particularly to backend code.
UI Improvements
You'll notice a refreshed UI that retains the original concept but has some notable enhancements. The service list view is now more visually engaging, it displays additional information in a more aesthetically pleasing manner. Both filtering and searching functionalities have been optimized for speed and user experience.
Service pages have been also redesigned to highlight key information at the top, with the KYC Level box always accessible. The display of service attributes is now more visually intuitive.
The request form, especially the Captcha, has undergone substantial improvements. The new self-made Captcha is robust, addressing the reliability issues encountered with the previous version.
Terms of Service Summarizer
A significant upgrade is the Terms of Service summarizer/reviewer, now powered by AI (GPT-4-turbo). It efficiently condenses each service's ToS, extracting and presenting critical points, including any warnings. Summaries are updated monthly, processing over 40 ToS pages via the OpenAI API using a self-crafted and thoroughly tested prompt.
Nostr Comments
I've integrated a comment section for each service using Nostr. For guidance on using this feature, visit the dedicated how-to page.
Database
The backend database has transitioned to pocketbase, an open-source Golang backend that has been a pleasure to work with. I maintain an updated fork of the Golang SDK for pocketbase at pluja/pocketbase.
Scoring
The scoring algorithm has also been refined to be more fair. Despite I had considered its removal due to the complexity it adds (it is very difficult to design a fair scoring system), some users highlighted its value, so I kept it. The updated algorithm is available open source.
Listings
Each listing has been re-evaluated, and the ones that were no longer operational were removed. New additions are included, and the backlog of pending services will be addressed progressively, since I still have access to the old database.
API
The API now offers more comprehensive data. For more details, check here.
About Page
The About page has been restructured for brevity and clarity.
Other Changes
Extensive changes have been implemented in the server-side logic, since the whole code base was re-written from the ground up. I may discuss these in a future post, but for now, I consider the current version to be just a bit beyond beta, and additional updates are planned in the coming weeks.
-
 @ 9be6a199:6e133301
2025-05-20 12:46:20
@ 9be6a199:6e133301
2025-05-20 12:46:20sadfsflkjsdflkdsjfglksjdfglksdaasdfsdfsdfsdfs
-
 @ 39cc53c9:27168656
2025-05-20 10:45:26
@ 39cc53c9:27168656
2025-05-20 10:45:26I'm launching a new service review section on this blog in collaboration with OrangeFren. These reviews are sponsored, yet the sponsorship does not influence the outcome of the evaluations. Reviews are done in advance, then, the service provider has the discretion to approve publication without modifications.
Sponsored reviews are independent from the kycnot.me list, being only part of the blog. The reviews have no impact on the scores of the listings or their continued presence on the list. Should any issues arise, I will not hesitate to remove any listing.
The review
WizardSwap is an instant exchange centred around privacy coins. It was launched in 2020 making it old enough to have weathered the 2021 bull run and the subsequent bearish year.
| Pros | Cons | |------|------| | Tor-friendly | Limited liquidity | | Guarantee of no KYC | Overly simplistic design | | Earn by providing liquidity | |
Rating: ★★★★★ Service Website: wizardswap.io
Liquidity
Right off the bat, we'll start off by pointing out that WizardSwap relies on its own liquidity reserves, meaning they aren't just a reseller of Binance or another exchange. They're also committed to a no-KYC policy, when asking them, they even promised they would rather refund a user their original coins, than force them to undergo any sort of verification.
On the one hand, full control over all their infrastructure gives users the most privacy and conviction about the KYC policies remaining in place.
On the other hand, this means the liquidity available for swapping isn't huge. At the time of testing we could only purchase at most about 0.73 BTC with XMR.
It's clear the team behind WizardSwap is aware of this shortfall and so they've come up with a solution unique among instant exchanges. They let you, the user, deposit any of the currencies they support into your account and earn a profit on the trades made using your liquidity.
Trading
Fees on WizardSwap are middle-of-the-pack. The normal fee is 2.2%. That's more than some exchanges that reserve the right to suddenly demand you undergo verification, yet less than half the fees on some other privacy-first exchanges. However as we mentioned in the section above you can earn almost all of that fee (2%) if you provide liquidity to WizardSwap.
It's good that with the current Bitcoin fee market their fees are constant regardless of how much, or how little, you send. This is in stark contrast with some of the alternative swap providers that will charge you a massive premium when attempting to swap small amounts of BTC away.
Test trades
Test trades are always performed without previous notice to the service provider.
During our testing we performed a few test trades and found that every single time WizardSwap immediately detected the incoming transaction and the amount we received was exactly what was quoted before depositing. The fees were inline with what WizardSwap advertises.

- Monero payment proof
- Bitcoin received
- Wizardswap TX link - it's possible that this link may cease to be valid at some point in the future.
ToS and KYC
WizardSwap does not have a Terms of Service or a Privacy Policy page, at least none that can be found by users. Instead, they offer a FAQ section where they addresses some basic questions.
The site does not mention any KYC or AML practices. It also does not specify how refunds are handled in case of failure. However, based on the FAQ section "What if I send funds after the offer expires?" it can be inferred that contacting support is necessary and network fees will be deducted from any refund.
UI & Tor
WizardSwap can be visited both via your usual browser and Tor Browser. Should you decide on the latter you'll find that the website works even with the most strict settings available in the Tor Browser (meaning no JavaScript).
However, when disabling Javascript you'll miss the live support chat, as well as automatic refreshing of the trade page. The lack of the first means that you will have no way to contact support from the trade page if anything goes wrong during your swap, although you can do so by mail.
One important thing to have in mind is that if you were to accidentally close the browser during the swap, and you did not save the swap ID or your browser history is disabled, you'll have no easy way to return to the trade. For this reason we suggest when you begin a trade to copy the url or ID to someplace safe, before sending any coins to WizardSwap.
The UI you'll be greeted by is simple, minimalist, and easy to navigate. It works well not just across browsers, but also across devices. You won't have any issues using this exchange on your phone.
Getting in touch
The team behind WizardSwap appears to be most active on X (formerly Twitter): https://twitter.com/WizardSwap_io
If you have any comments or suggestions about the exchange make sure to reach out to them. In the past they've been very receptive to user feedback, for instance a few months back WizardSwap was planning on removing DeepOnion, but the community behind that project got together ^1 and after reaching out WizardSwap reversed their decision ^2.
You can also contact them via email at:
support @ wizardswap . ioDisclaimer
None of the above should be understood as investment or financial advice. The views are our own only and constitute a faithful representation of our experience in using and investigating this exchange. This review is not a guarantee of any kind on the services rendered by the exchange. Do your own research before using any service.
-
 @ 9be6a199:6e133301
2025-05-20 12:45:08
@ 9be6a199:6e133301
2025-05-20 12:45:08sadfsflkjsdflkdsjfglksjdfglksd
-
 @ 6389be64:ef439d32
2025-01-13 21:50:59
@ 6389be64:ef439d32
2025-01-13 21:50:59Bitcoin is more than money, more than an asset, and more than a store of value. Bitcoin is a Prime Mover, an enabler and it ignites imaginations. It certainly fueled an idea in my mind. The idea integrates sensors, computational prowess, actuated machinery, power conversion, and electronic communications to form an autonomous, machined creature roaming forests and harvesting the most widespread and least energy-dense fuel source available. I call it the Forest Walker and it eats wood, and mines Bitcoin.
I know what you're thinking. Why not just put Bitcoin mining rigs where they belong: in a hosted facility sporting electricity from energy-dense fuels like natural gas, climate-controlled with excellent data piping in and out? Why go to all the trouble building a robot that digests wood creating flammable gasses fueling an engine to run a generator powering Bitcoin miners? It's all about synergy.
Bitcoin mining enables the realization of multiple, seemingly unrelated, yet useful activities. Activities considered un-profitable if not for Bitcoin as the Prime Mover. This is much more than simply mining the greatest asset ever conceived by humankind. It’s about the power of synergy, which Bitcoin plays only one of many roles. The synergy created by this system can stabilize forests' fire ecology while generating multiple income streams. That’s the realistic goal here and requires a brief history of American Forest management before continuing.
Smokey The Bear
In 1944, the Smokey Bear Wildfire Prevention Campaign began in the United States. “Only YOU can prevent forest fires” remains the refrain of the Ad Council’s longest running campaign. The Ad Council is a U.S. non-profit set up by the American Association of Advertising Agencies and the Association of National Advertisers in 1942. It would seem that the U.S. Department of the Interior was concerned about pesky forest fires and wanted them to stop. So, alongside a national policy of extreme fire suppression they enlisted the entire U.S. population to get onboard via the Ad Council and it worked. Forest fires were almost obliterated and everyone was happy, right? Wrong.
Smokey is a fantastically successful bear so forest fires became so few for so long that the fuel load - dead wood - in forests has become very heavy. So heavy that when a fire happens (and they always happen) it destroys everything in its path because the more fuel there is the hotter that fire becomes. Trees, bushes, shrubs, and all other plant life cannot escape destruction (not to mention homes and businesses). The soil microbiology doesn’t escape either as it is burned away even in deeper soils. To add insult to injury, hydrophobic waxy residues condense on the soil surface, forcing water to travel over the ground rather than through it eroding forest soils. Good job, Smokey. Well done, Sir!
Most terrestrial ecologies are “fire ecologies”. Fire is a part of these systems’ fuel load and pest management. Before we pretended to “manage” millions of acres of forest, fires raged over the world, rarely damaging forests. The fuel load was always too light to generate fires hot enough to moonscape mountainsides. Fires simply burned off the minor amounts of fuel accumulated since the fire before. The lighter heat, smoke, and other combustion gasses suppressed pests, keeping them in check and the smoke condensed into a plant growth accelerant called wood vinegar, not a waxy cap on the soil. These fires also cleared out weak undergrowth, cycled minerals, and thinned the forest canopy, allowing sunlight to penetrate to the forest floor. Without a fire’s heat, many pine tree species can’t sow their seed. The heat is required to open the cones (the seed bearing structure) of Spruce, Cypress, Sequoia, Jack Pine, Lodgepole Pine and many more. Without fire forests can’t have babies. The idea was to protect the forests, and it isn't working.
So, in a world of fire, what does an ally look like and what does it do?
Meet The Forest Walker
For the Forest Walker to work as a mobile, autonomous unit, a solid platform that can carry several hundred pounds is required. It so happens this chassis already exists but shelved.
Introducing the Legged Squad Support System (LS3). A joint project between Boston Dynamics, DARPA, and the United States Marine Corps, the quadrupedal robot is the size of a cow, can carry 400 pounds (180 kg) of equipment, negotiate challenging terrain, and operate for 24 hours before needing to refuel. Yes, it had an engine. Abandoned in 2015, the thing was too noisy for military deployment and maintenance "under fire" is never a high-quality idea. However, we can rebuild it to act as a platform for the Forest Walker; albeit with serious alterations. It would need to be bigger, probably. Carry more weight? Definitely. Maybe replace structural metal with carbon fiber and redesign much as 3D printable parts for more effective maintenance.
The original system has a top operational speed of 8 miles per hour. For our purposes, it only needs to move about as fast as a grazing ruminant. Without the hammering vibrations of galloping into battle, shocks of exploding mortars, and drunken soldiers playing "Wrangler of Steel Machines", time between failures should be much longer and the overall energy consumption much lower. The LS3 is a solid platform to build upon. Now it just needs to be pulled out of the mothballs, and completely refitted with outboard equipment.
The Small Branch Chipper
When I say “Forest fuel load” I mean the dead, carbon containing litter on the forest floor. Duff (leaves), fine-woody debris (small branches), and coarse woody debris (logs) are the fuel that feeds forest fires. Walk through any forest in the United States today and you will see quite a lot of these materials. Too much, as I have described. Some of these fuel loads can be 8 tons per acre in pine and hardwood forests and up to 16 tons per acre at active logging sites. That’s some big wood and the more that collects, the more combustible danger to the forest it represents. It also provides a technically unlimited fuel supply for the Forest Walker system.
The problem is that this detritus has to be chewed into pieces that are easily ingestible by the system for the gasification process (we’ll get to that step in a minute). What we need is a wood chipper attached to the chassis (the LS3); its “mouth”.
A small wood chipper handling material up to 2.5 - 3.0 inches (6.3 - 7.6 cm) in diameter would eliminate a substantial amount of fuel. There is no reason for Forest Walker to remove fallen trees. It wouldn’t have to in order to make a real difference. It need only identify appropriately sized branches and grab them. Once loaded into the chipper’s intake hopper for further processing, the beast can immediately look for more “food”. This is essentially kindling that would help ignite larger logs. If it’s all consumed by Forest Walker, then it’s not present to promote an aggravated conflagration.
I have glossed over an obvious question: How does Forest Walker see and identify branches and such? LiDaR (Light Detection and Ranging) attached to Forest Walker images the local area and feed those data to onboard computers for processing. Maybe AI plays a role. Maybe simple machine learning can do the trick. One thing is for certain: being able to identify a stick and cause robotic appendages to pick it up is not impossible.
Great! We now have a quadrupedal robot autonomously identifying and “eating” dead branches and other light, combustible materials. Whilst strolling through the forest, depleting future fires of combustibles, Forest Walker has already performed a major function of this system: making the forest safer. It's time to convert this low-density fuel into a high-density fuel Forest Walker can leverage. Enter the gasification process.
The Gassifier
The gasifier is the heart of the entire system; it’s where low-density fuel becomes the high-density fuel that powers the entire system. Biochar and wood vinegar are process wastes and I’ll discuss why both are powerful soil amendments in a moment, but first, what’s gasification?
Reacting shredded carbonaceous material at high temperatures in a low or no oxygen environment converts the biomass into biochar, wood vinegar, heat, and Synthesis Gas (Syngas). Syngas consists primarily of hydrogen, carbon monoxide, and methane. All of which are extremely useful fuels in a gaseous state. Part of this gas is used to heat the input biomass and keep the reaction temperature constant while the internal combustion engine that drives the generator to produce electrical power consumes the rest.
Critically, this gasification process is “continuous feed”. Forest Walker must intake biomass from the chipper, process it to fuel, and dump the waste (CO2, heat, biochar, and wood vinegar) continuously. It cannot stop. Everything about this system depends upon this continual grazing, digestion, and excretion of wastes just as a ruminal does. And, like a ruminant, all waste products enhance the local environment.
When I first heard of gasification, I didn’t believe that it was real. Running an electric generator from burning wood seemed more akin to “conspiracy fantasy” than science. Not only is gasification real, it’s ancient technology. A man named Dean Clayton first started experiments on gasification in 1699 and in 1901 gasification was used to power a vehicle. By the end of World War II, there were 500,000 Syngas powered vehicles in Germany alone because of fossil fuel rationing during the war. The global gasification market was $480 billion in 2022 and projected to be as much as $700 billion by 2030 (Vantage Market Research). Gasification technology is the best choice to power the Forest Walker because it’s self-contained and we want its waste products.
Biochar: The Waste
Biochar (AKA agricultural charcoal) is fairly simple: it’s almost pure, solid carbon that resembles charcoal. Its porous nature packs large surface areas into small, 3 dimensional nuggets. Devoid of most other chemistry, like hydrocarbons (methane) and ash (minerals), biochar is extremely lightweight. Do not confuse it with the charcoal you buy for your grill. Biochar doesn’t make good grilling charcoal because it would burn too rapidly as it does not contain the multitude of flammable components that charcoal does. Biochar has several other good use cases. Water filtration, water retention, nutrient retention, providing habitat for microscopic soil organisms, and carbon sequestration are the main ones that we are concerned with here.
Carbon has an amazing ability to adsorb (substances stick to and accumulate on the surface of an object) manifold chemistries. Water, nutrients, and pollutants tightly bind to carbon in this format. So, biochar makes a respectable filter and acts as a “battery” of water and nutrients in soils. Biochar adsorbs and holds on to seven times its weight in water. Soil containing biochar is more drought resilient than soil without it. Adsorbed nutrients, tightly sequestered alongside water, get released only as plants need them. Plants must excrete protons (H+) from their roots to disgorge water or positively charged nutrients from the biochar's surface; it's an active process.
Biochar’s surface area (where adsorption happens) can be 500 square meters per gram or more. That is 10% larger than an official NBA basketball court for every gram of biochar. Biochar’s abundant surface area builds protective habitats for soil microbes like fungi and bacteria and many are critical for the health and productivity of the soil itself.
The “carbon sequestration” component of biochar comes into play where “carbon credits” are concerned. There is a financial market for carbon. Not leveraging that market for revenue is foolish. I am climate agnostic. All I care about is that once solid carbon is inside the soil, it will stay there for thousands of years, imparting drought resiliency, fertility collection, nutrient buffering, and release for that time span. I simply want as much solid carbon in the soil because of the undeniably positive effects it has, regardless of any climactic considerations.
Wood Vinegar: More Waste
Another by-product of the gasification process is wood vinegar (Pyroligneous acid). If you have ever seen Liquid Smoke in the grocery store, then you have seen wood vinegar. Principally composed of acetic acid, acetone, and methanol wood vinegar also contains ~200 other organic compounds. It would seem intuitive that condensed, liquefied wood smoke would at least be bad for the health of all living things if not downright carcinogenic. The counter intuition wins the day, however. Wood vinegar has been used by humans for a very long time to promote digestion, bowel, and liver health; combat diarrhea and vomiting; calm peptic ulcers and regulate cholesterol levels; and a host of other benefits.
For centuries humans have annually burned off hundreds of thousands of square miles of pasture, grassland, forest, and every other conceivable terrestrial ecosystem. Why is this done? After every burn, one thing becomes obvious: the almost supernatural growth these ecosystems exhibit after the burn. How? Wood vinegar is a component of this growth. Even in open burns, smoke condenses and infiltrates the soil. That is when wood vinegar shows its quality.
This stuff beefs up not only general plant growth but seed germination as well and possesses many other qualities that are beneficial to plants. It’s a pesticide, fungicide, promotes beneficial soil microorganisms, enhances nutrient uptake, and imparts disease resistance. I am barely touching a long list of attributes here, but you want wood vinegar in your soil (alongside biochar because it adsorbs wood vinegar as well).
The Internal Combustion Engine
Conversion of grazed forage to chemical, then mechanical, and then electrical energy completes the cycle. The ICE (Internal Combustion Engine) converts the gaseous fuel output from the gasifier to mechanical energy, heat, water vapor, and CO2. It’s the mechanical energy of a rotating drive shaft that we want. That rotation drives the electric generator, which is the heartbeat we need to bring this monster to life. Luckily for us, combined internal combustion engine and generator packages are ubiquitous, delivering a defined energy output given a constant fuel input. It’s the simplest part of the system.
The obvious question here is whether the amount of syngas provided by the gasification process will provide enough energy to generate enough electrons to run the entire system or not. While I have no doubt the energy produced will run Forest Walker's main systems the question is really about the electrons left over. Will it be enough to run the Bitcoin mining aspect of the system? Everything is a budget.
CO2 Production For Growth
Plants are lollipops. No matter if it’s a tree or a bush or a shrubbery, the entire thing is mostly sugar in various formats but mostly long chain carbohydrates like lignin and cellulose. Plants need three things to make sugar: CO2, H2O and light. In a forest, where tree densities can be quite high, CO2 availability becomes a limiting growth factor. It’d be in the forest interests to have more available CO2 providing for various sugar formation providing the organism with food and structure.
An odd thing about tree leaves, the openings that allow gasses like the ever searched for CO2 are on the bottom of the leaf (these are called stomata). Not many stomata are topside. This suggests that trees and bushes have evolved to find gasses like CO2 from below, not above and this further suggests CO2 might be in higher concentrations nearer the soil.
The soil life (bacterial, fungi etc.) is constantly producing enormous amounts of CO2 and it would stay in the soil forever (eventually killing the very soil life that produces it) if not for tidal forces. Water is everywhere and whether in pools, lakes, oceans or distributed in “moist” soils water moves towards to the moon. The water in the soil and also in the water tables below the soil rise toward the surface every day. When the water rises, it expels the accumulated gasses in the soil into the atmosphere and it’s mostly CO2. It’s a good bet on how leaves developed high populations of stomata on the underside of leaves. As the water relaxes (the tide goes out) it sucks oxygenated air back into the soil to continue the functions of soil life respiration. The soil “breathes” albeit slowly.
The gasses produced by the Forest Walker’s internal combustion engine consist primarily of CO2 and H2O. Combusting sugars produce the same gasses that are needed to construct the sugars because the universe is funny like that. The Forest Walker is constantly laying down these critical construction elements right where the trees need them: close to the ground to be gobbled up by the trees.
The Branch Drones
During the last ice age, giant mammals populated North America - forests and otherwise. Mastodons, woolly mammoths, rhinos, short-faced bears, steppe bison, caribou, musk ox, giant beavers, camels, gigantic ground-dwelling sloths, glyptodons, and dire wolves were everywhere. Many were ten to fifteen feet tall. As they crashed through forests, they would effectively cleave off dead side-branches of trees, halting the spread of a ground-based fire migrating into the tree crown ("laddering") which is a death knell for a forest.
These animals are all extinct now and forests no longer have any manner of pruning services. But, if we build drones fitted with cutting implements like saws and loppers, optical cameras and AI trained to discern dead branches from living ones, these drones could effectively take over pruning services by identifying, cutting, and dropping to the forest floor, dead branches. The dropped branches simply get collected by the Forest Walker as part of its continual mission.
The drones dock on the back of the Forest Walker to recharge their batteries when low. The whole scene would look like a grazing cow with some flies bothering it. This activity breaks the link between a relatively cool ground based fire and the tree crowns and is a vital element in forest fire control.
The Bitcoin Miner
Mining is one of four monetary incentive models, making this system a possibility for development. The other three are US Dept. of the Interior, township, county, and electrical utility company easement contracts for fuel load management, global carbon credits trading, and data set sales. All the above depends on obvious questions getting answered. I will list some obvious ones, but this is not an engineering document and is not the place for spreadsheets. How much Bitcoin one Forest Walker can mine depends on everything else. What amount of biomass can we process? Will that biomass flow enough Syngas to keep the lights on? Can the chassis support enough mining ASICs and supporting infrastructure? What does that weigh and will it affect field performance? How much power can the AC generator produce?
Other questions that are more philosophical persist. Even if a single Forest Walker can only mine scant amounts of BTC per day, that pales to how much fuel material it can process into biochar. We are talking about millions upon millions of forested acres in need of fuel load management. What can a single Forest Walker do? I am not thinking in singular terms. The Forest Walker must operate as a fleet. What could 50 do? 500?
What is it worth providing a service to the world by managing forest fuel loads? Providing proof of work to the global monetary system? Seeding soil with drought and nutrient resilience by the excretion, over time, of carbon by the ton? What did the last forest fire cost?
The Mesh Network
What could be better than one bitcoin mining, carbon sequestering, forest fire squelching, soil amending behemoth? Thousands of them, but then they would need to be able to talk to each other to coordinate position, data handling, etc. Fitted with a mesh networking device, like goTenna or Meshtastic LoRa equipment enables each Forest Walker to communicate with each other.
Now we have an interconnected fleet of Forest Walkers relaying data to each other and more importantly, aggregating all of that to the last link in the chain for uplink. Well, at least Bitcoin mining data. Since block data is lightweight, transmission of these data via mesh networking in fairly close quartered environs is more than doable. So, how does data transmit to the Bitcoin Network? How do the Forest Walkers get the previous block data necessary to execute on mining?
Back To The Chain
Getting Bitcoin block data to and from the network is the last puzzle piece. The standing presumption here is that wherever a Forest Walker fleet is operating, it is NOT within cell tower range. We further presume that the nearest Walmart Wi-Fi is hours away. Enter the Blockstream Satellite or something like it.
A separate, ground-based drone will have two jobs: To stay as close to the nearest Forest Walker as it can and to provide an antennae for either terrestrial or orbital data uplink. Bitcoin-centric data is transmitted to the "uplink drone" via the mesh networked transmitters and then sent on to the uplink and the whole flow goes in the opposite direction as well; many to one and one to many.
We cannot transmit data to the Blockstream satellite, and it will be up to Blockstream and companies like it to provide uplink capabilities in the future and I don't doubt they will. Starlink you say? What’s stopping that company from filtering out block data? Nothing because it’s Starlink’s system and they could decide to censor these data. It seems we may have a problem sending and receiving Bitcoin data in back country environs.
But, then again, the utility of this system in staunching the fuel load that creates forest fires is extremely useful around forested communities and many have fiber, Wi-Fi and cell towers. These communities could be a welcoming ground zero for first deployments of the Forest Walker system by the home and business owners seeking fire repression. In the best way, Bitcoin subsidizes the safety of the communities.
Sensor Packages
LiDaR
The benefit of having a Forest Walker fleet strolling through the forest is the never ending opportunity for data gathering. A plethora of deployable sensors gathering hyper-accurate data on everything from temperature to topography is yet another revenue generator. Data is valuable and the Forest Walker could generate data sales to various government entities and private concerns.
LiDaR (Light Detection and Ranging) can map topography, perform biomass assessment, comparative soil erosion analysis, etc. It so happens that the Forest Walker’s ability to “see,” to navigate about its surroundings, is LiDaR driven and since it’s already being used, we can get double duty by harvesting that data for later use. By using a laser to send out light pulses and measuring the time it takes for the reflection of those pulses to return, very detailed data sets incrementally build up. Eventually, as enough data about a certain area becomes available, the data becomes useful and valuable.
Forestry concerns, both private and public, often use LiDaR to build 3D models of tree stands to assess the amount of harvest-able lumber in entire sections of forest. Consulting companies offering these services charge anywhere from several hundred to several thousand dollars per square kilometer for such services. A Forest Walker generating such assessments on the fly while performing its other functions is a multi-disciplinary approach to revenue generation.
pH, Soil Moisture, and Cation Exchange Sensing
The Forest Walker is quadrupedal, so there are four contact points to the soil. Why not get a pH data point for every step it takes? We can also gather soil moisture data and cation exchange capacities at unheard of densities because of sampling occurring on the fly during commission of the system’s other duties. No one is going to build a machine to do pH testing of vast tracts of forest soils, but that doesn’t make the data collected from such an endeavor valueless. Since the Forest Walker serves many functions at once, a multitude of data products can add to the return on investment component.
Weather Data
Temperature, humidity, pressure, and even data like evapotranspiration gathered at high densities on broad acre scales have untold value and because the sensors are lightweight and don’t require large power budgets, they come along for the ride at little cost. But, just like the old mantra, “gas, grass, or ass, nobody rides for free”, these sensors provide potential revenue benefits just by them being present.
I’ve touched on just a few data genres here. In fact, the question for universities, governmental bodies, and other institutions becomes, “How much will you pay us to attach your sensor payload to the Forest Walker?”
Noise Suppression
Only you can prevent Metallica filling the surrounds with 120 dB of sound. Easy enough, just turn the car stereo off. But what of a fleet of 50 Forest Walkers operating in the backcountry or near a township? 500? 5000? Each one has a wood chipper, an internal combustion engine, hydraulic pumps, actuators, and more cooling fans than you can shake a stick at. It’s a walking, screaming fire-breathing dragon operating continuously, day and night, twenty-four hours a day, three hundred sixty-five days a year. The sound will negatively affect all living things and that impacts behaviors. Serious engineering consideration and prowess must deliver a silencing blow to the major issue of noise.
It would be foolish to think that a fleet of Forest Walkers could be silent, but if not a major design consideration, then the entire idea is dead on arrival. Townships would not allow them to operate even if they solved the problem of widespread fuel load and neither would governmental entities, and rightly so. Nothing, not man nor beast, would want to be subjected to an eternal, infernal scream even if it were to end within days as the fleet moved further away after consuming what it could. Noise and heat are the only real pollutants of this system; taking noise seriously from the beginning is paramount.
Fire Safety
A “fire-breathing dragon” is not the worst description of the Forest Walker. It eats wood, combusts it at very high temperatures and excretes carbon; and it does so in an extremely flammable environment. Bad mix for one Forest Walker, worse for many. One must take extreme pains to ensure that during normal operation, a Forest Walker could fall over, walk through tinder dry brush, or get pounded into the ground by a meteorite from Krypton and it wouldn’t destroy epic swaths of trees and baby deer. I envision an ultimate test of a prototype to include dowsing it in grain alcohol while it’s wrapped up in toilet paper like a pledge at a fraternity party. If it runs for 72 hours and doesn’t set everything on fire, then maybe outside entities won’t be fearful of something that walks around forests with a constant fire in its belly.
The Wrap
How we think about what can be done with and adjacent to Bitcoin is at least as important as Bitcoin’s economic standing itself. For those who will tell me that this entire idea is without merit, I say, “OK, fine. You can come up with something, too.” What can we plug Bitcoin into that, like a battery, makes something that does not work, work? That’s the lesson I get from this entire exercise. No one was ever going to hire teams of humans to go out and "clean the forest". There's no money in that. The data collection and sales from such an endeavor might provide revenues over the break-even point but investment demands Alpha in this day and age. But, plug Bitcoin into an almost viable system and, voilà! We tip the scales to achieve lift-off.
Let’s face it, we haven’t scratched the surface of Bitcoin’s forcing function on our minds. Not because it’s Bitcoin, but because of what that invention means. The question that pushes me to approach things this way is, “what can we create that one system’s waste is another system’s feedstock?” The Forest Walker system’s only real waste is the conversion of low entropy energy (wood and syngas) into high entropy energy (heat and noise). All other output is beneficial to humanity.
Bitcoin, I believe, is the first product of a new mode of human imagination. An imagination newly forged over the past few millennia of being lied to, stolen from, distracted and otherwise mis-allocated to a black hole of the nonsensical. We are waking up.
What I have presented is not science fiction. Everything I have described here is well within the realm of possibility. The question is one of viability, at least in terms of the detritus of the old world we find ourselves departing from. This system would take a non-trivial amount of time and resources to develop. I think the system would garner extensive long-term contracts from those who have the most to lose from wildfires, the most to gain from hyperaccurate data sets, and, of course, securing the most precious asset in the world. Many may not see it that way, for they seek Alpha and are therefore blind to other possibilities. Others will see only the possibilities; of thinking in a new way, of looking at things differently, and dreaming of what comes next.
-
 @ 39cc53c9:27168656
2025-05-20 10:45:24
@ 39cc53c9:27168656
2025-05-20 10:45:24Bitcoin enthusiasts frequently and correctly remark how much value it adds to Bitcoin not to have a face, a leader, or a central authority behind it. This particularity means there isn't a single person to exert control over, or a single human point of failure who could become corrupt or harmful to the project.
Because of this, it is said that no other coin can be equally valuable as Bitcoin in terms of decentralization and trustworthiness. Bitcoin is unique not just for being first, but also because of how the events behind its inception developed. This implies that, from Bitcoin onwards, any coin created would have been created by someone, consequently having an authority behind it. For this and some other reasons, some people refer to Bitcoin as "The Immaculate Conception".
While other coins may have their own unique features and advantages, they may not be able to replicate Bitcoin's community-driven nature. However, one other cryptocurrency shares a similar story of mystery behind its creation: Monero.
History of Monero
Bytecoin and CryptoNote
In March 2014, a Bitcointalk thread titled "Bytecoin. Secure, private, untraceable since 2012" was initiated by a user under the nickname "DStrange"^1^. DStrange presented Bytecoin (BCN) as a unique cryptocurrency, in operation since July 2012. Unlike Bitcoin, it employed a new algorithm known as CryptoNote.
DStrange apparently stumbled upon the Bytecoin website by chance while mining a dying bitcoin fork, and decided to create a thread on Bitcointalk^1^. This sparked curiosity among some users, who wondered how could Bytecoin remain unnoticed since its alleged launch in 2012 until then^2^.
Some time after, a user brought up the "CryptoNote v2.0" whitepaper for the first time, underlining its innovative features^4^. Authored by the pseudonymous Nicolas van Saberhagen in October 2013, the CryptoNote v2 whitepaper^5^ highlighted the traceability and privacy problems in Bitcoin. Saberhagen argued that these flaws could not be quickly fixed, suggesting it would be more efficient to start a new project rather than trying to patch the original^5^, an statement simmilar to the one from Satoshi Nakamoto^6^.
Checking with Saberhagen's digital signature, the release date of the whitepaper seemed correct, which would mean that Cryptonote (v1) was created in 2012^7^, although there's an important detail: "Signing time is from the clock on the signer's computer" ^9^.
Moreover, the whitepaper v1 contains a footnote link to a Bitcointalk post dated May 5, 2013^10^, making it impossible for the whitepaper to have been signed and released on December 12, 2012.
As the narrative developed, users discovered that a significant 80% portion of Bytecoin had been pre-mined^11^ and blockchain dates seemed to be faked to make it look like it had been operating since 2012, leading to controversy surrounding the project.
The origins of CryptoNote and Bytecoin remain mysterious, leaving suspicions of a possible scam attempt, although the whitepaper had a good amount of work and thought on it.
The fork
In April 2014, the Bitcointalk user
thankful_for_today, who had also participated in the Bytecoin thread^12^, announced plans to launch a Bytecoin fork named Bitmonero^13^.The primary motivation behind this fork was "Because there is a number of technical and marketing issues I wanted to do differently. And also because I like ideas and technology and I want it to succeed"^14^. This time Bitmonero did things different from Bytecoin: there was no premine or instamine, and no portion of the block reward went to development.
However, thankful_for_today proposed controversial changes that the community disagreed with. Johnny Mnemonic relates the events surrounding Bitmonero and thankful_for_today in a Bitcointalk comment^15^:
When thankful_for_today launched BitMonero [...] he ignored everything that was discussed and just did what he wanted. The block reward was considerably steeper than what everyone was expecting. He also moved forward with 1-minute block times despite everyone's concerns about the increase of orphan blocks. He also didn't address the tail emission concern that should've (in my opinion) been in the code at launch time. Basically, he messed everything up. Then, he disappeared.
After disappearing for a while, thankful_for_today returned to find that the community had taken over the project. Johnny Mnemonic continues:
I, and others, started working on new forks that were closer to what everyone else was hoping for. [...] it was decided that the BitMonero project should just be taken over. There were like 9 or 10 interested parties at the time if my memory is correct. We voted on IRC to drop the "bit" from BitMonero and move forward with the project. Thankful_for_today suddenly resurfaced, and wasn't happy to learn the community had assumed control of the coin. He attempted to maintain his own fork (still calling it "BitMonero") for a while, but that quickly fell into obscurity.
The unfolding of these events show us the roots of Monero. Much like Satoshi Nakamoto, the creators behind CryptoNote/Bytecoin and thankful_for_today remain a mystery^17^, having disappeared without a trace. This enigma only adds to Monero's value.
Since community took over development, believing in the project's potential and its ability to be guided in a better direction, Monero was given one of Bitcoin's most important qualities: a leaderless nature. With no single face or entity directing its path, Monero is safe from potential corruption or harm from a "central authority".
The community continued developing Monero until today. Since then, Monero has undergone a lot of technological improvements, migrations and achievements such as RingCT and RandomX. It also has developed its own Community Crowdfundinc System, conferences such as MoneroKon and Monerotopia are taking place every year, and has a very active community around it.
Monero continues to develop with goals of privacy and security first, ease of use and efficiency second. ^16^
This stands as a testament to the power of a dedicated community operating without a central figure of authority. This decentralized approach aligns with the original ethos of cryptocurrency, making Monero a prime example of community-driven innovation. For this, I thank all the people involved in Monero, that lead it to where it is today.
If you find any information that seems incorrect, unclear or any missing important events, please contact me and I will make the necessary changes.
Sources of interest
- https://forum.getmonero.org/20/general-discussion/211/history-of-monero
- https://monero.stackexchange.com/questions/852/what-is-the-origin-of-monero-and-its-relationship-to-bytecoin
- https://en.wikipedia.org/wiki/Monero
- https://bitcointalk.org/index.php?topic=583449.0
- https://bitcointalk.org/index.php?topic=563821.0
- https://bitcointalk.org/index.php?action=profile;u=233561
- https://bitcointalk.org/index.php?topic=512747.0
- https://bitcointalk.org/index.php?topic=740112.0
- https://monero.stackexchange.com/a/1024
- https://inspec2t-project.eu/cryptocurrency-with-a-focus-on-anonymity-these-facts-are-known-about-monero/
- https://medium.com/coin-story/coin-perspective-13-riccardo-spagni-69ef82907bd1
- https://www.getmonero.org/resources/about/
- https://www.wired.com/2017/01/monero-drug-dealers-cryptocurrency-choice-fire/
- https://www.monero.how/why-monero-vs-bitcoin
- https://old.reddit.com/r/Monero/comments/u8e5yr/satoshi_nakamoto_talked_about_privacy_features/
-
 @ 9be6a199:6e133301
2025-05-20 12:44:22
@ 9be6a199:6e133301
2025-05-20 12:44:22 -
 @ 39cc53c9:27168656
2025-05-20 10:45:18
@ 39cc53c9:27168656
2025-05-20 10:45:18“The future is there... staring back at us. Trying to make sense of the fiction we will have become.” — William Gibson.
This month is the 4th anniversary of kycnot.me. Thank you for being here.
Fifteen years ago, Satoshi Nakamoto introduced Bitcoin, a peer-to-peer electronic cash system: a decentralized currency free from government and institutional control. Nakamoto's whitepaper showed a vision for a financial system based on trustless transactions, secured by cryptography. Some time forward and KYC (Know Your Customer), AML (Anti-Money Laundering), and CTF (Counter-Terrorism Financing) regulations started to come into play.
What a paradox: to engage with a system designed for decentralization, privacy, and independence, we are forced to give away our personal details. Using Bitcoin in the economy requires revealing your identity, not just to the party you interact with, but also to third parties who must track and report the interaction. You are forced to give sensitive data to entities you don't, can't, and shouldn't trust. Information can never be kept 100% safe; there's always a risk. Information is power, who knows about you has control over you.
Information asymmetry creates imbalances of power. When entities have detailed knowledge about individuals, they can manipulate, influence, or exploit this information to their advantage. The accumulation of personal data by corporations and governments enables extensive surveillances.
Such practices, moreover, exclude individuals from traditional economic systems if their documentation doesn't meet arbitrary standards, reinforcing a dystopian divide. Small businesses are similarly burdened by the costs of implementing these regulations, hindering free market competition^1:

How will they keep this information safe? Why do they need my identity? Why do they force businesses to enforce such regulations? It's always for your safety, to protect you from the "bad". Your life is perpetually in danger: terrorists, money launderers, villains... so the government steps in to save us.
‟Hush now, baby, baby, don't you cry Mamma's gonna make all of your nightmares come true Mamma's gonna put all of her fears into you Mamma's gonna keep you right here, under her wing She won't let you fly, but she might let you sing Mamma's gonna keep baby cosy and warm” — Mother, Pink Floyd
We must resist any attack on our privacy and freedom. To do this, we must collaborate.
If you have a service, refuse to ask for KYC; find a way. Accept cryptocurrencies like Bitcoin and Monero. Commit to circular economies. Remove the need to go through the FIAT system. People need fiat money to use most services, but we can change that.
If you're a user, donate to and prefer using services that accept such currencies. Encourage your friends to accept cryptocurrencies as well. Boycott FIAT system to the greatest extent you possibly can.
This may sound utopian, but it can be achieved. This movement can't be stopped. Go kick the hornet's nest.
“We must defend our own privacy if we expect to have any. We must come together and create systems which allow anonymous transactions to take place. People have been defending their own privacy for centuries with whispers, darkness, envelopes, closed doors, secret handshakes, and couriers. The technologies of the past did not allow for strong privacy, but electronic technologies do.” — Eric Hughes, A Cypherpunk's Manifesto
The anniversary
Four years ago, I began exploring ways to use crypto without KYC. I bookmarked a few favorite services and thought sharing them to the world might be useful. That was the first version of kycnot.me — a simple list of about 15 services. Since then, I've added services, rewritten it three times, and improved it to what it is now.
kycnot.me has remained 100% independent and 100% open source^2 all these years. I've received offers to buy the site, all of which I have declined and will continue to decline. It has been DDoS attacked many times, but we made it through. I have also rewritten the whole site almost once per year (three times in four years).
The code and scoring algorithm are open source (contributions are welcome) and I can't arbitrarly change a service's score without adding or removing attributes, making any arbitrary alterations obvious if they were fake. You can even see the score summary for any service's score.
I'm a one-person team, dedicating my free time to this project. I hope to keep doing so for many more years. Again, thank you for being part of this.
-
 @ f85b9c2c:d190bcff
2025-05-20 12:41:35
@ f85b9c2c:d190bcff
2025-05-20 12:41:35 Solana (SOL) is acquiring popularity in the crypto world for its speed and flexibility.It's rapidly gaining ground on established blockchains, grabbing investor interest.
Solana (SOL) is acquiring popularity in the crypto world for its speed and flexibility.It's rapidly gaining ground on established blockchains, grabbing investor interest.History Of Solana Anatoly Yakovenko, once a Qualcomm executive, formulated the concept for Solana in 2017. A town on the Southern California coast inspired the name. Yakovenko wanted a swifter, more reliable blockchain network to address the limitations of existing onesat that time. Solana is based in San Francisco, California, at the headquarters of Solana Labs. Solana was launched in March 2020, making a major step in the advancement of blockchain technology.
What Is Solana? Solana is a blockchain network built for speed and affordability.This versatility makes it useful for DeFi, NFTs, and more. Solana operates on its own independent blockchain network with SOL as its native token and infrastructure to power its operations. It functions as a self-sufficient ecosystem, independent of any other existing blockchain network.
How Does Solana Work? Unlike normal blockchains that usually rely on the Proof-of-Work mechanism, Solana uses another approach. It combines two mechanisms: 1.Proof-of-Stake: It lets operators secure the network by putting SOL tokens at stake. These operators are entrusted with adding new blocks to the blockchain and are rewarded for their contribution.
2.Proof-of-History: It helps eliminates the need for communications between operators and boosts transaction processing speed.
Conclusion The mix of these mechanisms is a key factor behind Solana’s reputation for superior speed. Of course, it uses other technical aspects that contribute to its efficiency, but PoS and PoH play a critical role.
-
 @ 3f770d65:7a745b24
2025-01-12 21:03:36
@ 3f770d65:7a745b24
2025-01-12 21:03:36I’ve been using Notedeck for several months, starting with its extremely early and experimental alpha versions, all the way to its current, more stable alpha releases. The journey has been fascinating, as I’ve had the privilege of watching it evolve from a concept into a functional and promising tool.
In its earliest stages, Notedeck was raw—offering glimpses of its potential but still far from practical for daily use. Even then, the vision behind it was clear: a platform designed to redefine how we interact with Nostr by offering flexibility and power for all users.
I'm very bullish on Notedeck. Why? Because Will Casarin is making it! Duh! 😂
Seriously though, if we’re reimagining the web and rebuilding portions of the Internet, it’s important to recognize the potential of Notedeck. If Nostr is reimagining the web, then Notedeck is reimagining the Nostr client.
Notedeck isn’t just another Nostr app—it’s more a Nostr browser that functions more like an operating system with micro-apps. How cool is that?
Much like how Google's Chrome evolved from being a web browser with a task manager into ChromeOS, a full blown operating system, Notedeck aims to transform how we interact with the Nostr. It goes beyond individual apps, offering a foundation for a fully integrated ecosystem built around Nostr.
As a Nostr evangelist, I love to scream INTEROPERABILITY and tout every application's integrations. Well, Notedeck has the potential to be one of the best platforms to showcase these integrations in entirely new and exciting ways.
Do you want an Olas feed of images? Add the media column.
Do you want a feed of live video events? Add the zap.stream column.
Do you want Nostr Nests or audio chats? Add that column to your Notedeck.
Git? Email? Books? Chat and DMs? It's all possible.
Not everyone wants a super app though, and that’s okay. As with most things in the Nostr ecosystem, flexibility is key. Notedeck gives users the freedom to choose how they engage with it—whether it’s simply following hashtags or managing straightforward feeds. You'll be able to tailor Notedeck to fit your needs, using it as extensively or minimally as you prefer.
Notedeck is designed with a local-first approach, utilizing Nostr content stored directly on your device via the local nostrdb. This will enable a plethora of advanced tools such as search and filtering, the creation of custom feeds, and the ability to develop personalized algorithms across multiple Notedeck micro-applications—all with unparalleled flexibility.
Notedeck also supports multicast. Let's geek out for a second. Multicast is a method of communication where data is sent from one source to multiple destinations simultaneously, but only to devices that wish to receive the data. Unlike broadcast, which sends data to all devices on a network, multicast targets specific receivers, reducing network traffic. This is commonly used for efficient data distribution in scenarios like streaming, conferencing, or large-scale data synchronization between devices.
In a local first world where each device holds local copies of your nostr nodes, and each device transparently syncs with each other on the local network, each node becomes a backup. Your data becomes antifragile automatically. When a node goes down it can resync and recover from other nodes. Even if not all nodes have a complete collection, negentropy can pull down only what is needed from each device. All this can be done without internet.
-Will Casarin
In the context of Notedeck, multicast would allow multiple devices to sync their Nostr nodes with each other over a local network without needing an internet connection. Wild.
Notedeck aims to offer full customization too, including the ability to design and share custom skins, much like Winamp. Users will also be able to create personalized columns and, in the future, share their setups with others. This opens the door for power users to craft tailored Nostr experiences, leveraging their expertise in the protocol and applications. By sharing these configurations as "Starter Decks," they can simplify onboarding and showcase the best of Nostr’s ecosystem.
Nostr’s “Other Stuff” can often be difficult to discover, use, or understand. Many users doesn't understand or know how to use web browser extensions to login to applications. Let's not even get started with nsecbunkers. Notedeck will address this challenge by providing a native experience that brings these lesser-known applications, tools, and content into a user-friendly and accessible interface, making exploration seamless. However, that doesn't mean Notedeck should disregard power users that want to use nsecbunkers though - hint hint.
For anyone interested in watching Nostr be developed live, right before your very eyes, Notedeck’s progress serves as a reminder of what’s possible when innovation meets dedication. The current alpha is already demonstrating its ability to handle complex use cases, and I’m excited to see how it continues to grow as it moves toward a full release later this year.
-
 @ a93d7cd3:ae5ce5dd
2025-05-20 10:16:55
@ a93d7cd3:ae5ce5dd
2025-05-20 10:16:55Test Nostr
-
 @ cd17b2d6:8cc53332
2025-05-20 10:15:09
@ cd17b2d6:8cc53332
2025-05-20 10:15:09🚀 Instantly Send Spendable Flash BTC, ETH, & USDT — Fully Blockchain-Verifiable!
Welcome to the cutting edge of crypto innovation: the ultimate tool for sending spendable Flash Bitcoin (BTC), Ethereum (ETH), and USDT transactions. Our advanced blockchain simulation technology employs 🔥 Race/Finney-style mechanisms, producing coins indistinguishable from authentic blockchain-confirmed tokens. Your transactions are instantly trackable and fully spendable for durations from 60 to 360 days!
🌐 Visit cryptoflashingtool.com for complete details.
🌟 Why Choose Our Crypto Flashing Service? Crypto Flashing is perfect for crypto enthusiasts, blockchain developers, ethical hackers, security professionals, and digital entrepreneurs looking for authenticity combined with unparalleled flexibility.
🎯 Our Crypto Flashing Features: ✅ Instant Blockchain Verification: Transactions appear completely authentic, complete with real blockchain confirmations, transaction IDs, and wallet addresses.
🔒 Maximum Security & Privacy: Fully compatible with VPNs, TOR, and proxy servers, ensuring absolute anonymity and protection.
🖥️ Easy-to-Use Software: Designed for Windows, our intuitive platform suits both beginners and experts, with detailed, step-by-step instructions provided.
📅 Customizable Flash Durations: Control your transaction lifespan precisely, from 60 to 360 days.
🔄 Universal Wallet Compatibility: Instantly flash BTC, ETH, and USDT tokens to SegWit, Legacy, or BCH32 wallets.
💱 Spendable on Top Exchanges: Flash coins seamlessly accepted on leading exchanges like Kraken and Huobi.
📊 Proven Track Record: ✅ Over 79 Billion flash transactions completed. ✅ 3000+ satisfied customers worldwide. ✅ 42 active blockchain nodes for fast, reliable transactions. 📌 Simple Step-by-Step Flashing Process: Step 1️⃣: Enter Transaction Details
Choose coin (BTC, ETH, USDT: TRC-20, ERC-20, BEP-20) Specify amount & flash duration Provide wallet address (validated automatically) Step 2️⃣: Complete Payment & Verification
Pay using the cryptocurrency you wish to flash Scan the QR code or paste the payment address Upload payment proof (transaction hash & screenshot) Step 3️⃣: Initiate Flash Transaction
Our technology simulates blockchain confirmations instantly Flash transaction appears authentic within seconds Step 4️⃣: Verify & Spend Immediately
Access your flashed crypto instantly Easily verify transactions via provided blockchain explorer links 🛡️ Why Our Technology is Trusted: 🔗 Race/Finney Attack Logic: Creates realistic blockchain headers. 🖥️ Private iNode Cluster: Guarantees fast synchronization and reliable transactions. ⏰ Live Timer System: Ensures fresh wallet addresses and transaction legitimacy. 🔍 Genuine Blockchain TX IDs: Authentic transaction IDs included with every flash ❓ Frequently Asked Questions: Is flashing secure? ✅ Yes, encrypted with full VPN/proxy support. Can I flash from multiple devices? ✅ Yes, up to 5 Windows PCs per license. Are chargebacks possible? ❌ No, flash transactions are irreversible. How long are flash coins spendable? ✅ From 60–360 days, based on your chosen plan. Verification after expiry? ❌ Transactions can’t be verified after the expiry. Support available? ✅ Yes, 24/7 support via Telegram & WhatsApp.
🔐 Transparent, Reliable & Highly Reviewed:
CryptoFlashingTool.com operates independently, providing unmatched transparency and reliability. Check out our glowing reviews on ScamAdvisor and leading crypto forums!
📲 Get in Touch Now: 📞 WhatsApp: +1 770 666 2531 ✈️ Telegram: @cryptoflashingtool
🎉 Ready to Start?
💰 Buy Flash Coins Now 🖥️ Get Your Flashing Software
Experience the smartest, safest, and most powerful crypto flashing solution on the market today!
CryptoFlashingTool.com — Flash Crypto Like a Pro.
Instantly Send Spendable Flash BTC, ETH, & USDT — Fully Blockchain-Verifiable!
Welcome to the cutting edge of crypto innovation: the ultimate tool for sending spendable Flash Bitcoin (BTC), Ethereum (ETH), and USDT transactions. Our advanced blockchain simulation technology employs
Race/Finney-style mechanisms, producing coins indistinguishable from authentic blockchain-confirmed tokens. Your transactions are instantly trackable and fully spendable for durations from 60 to 360 days!
Visit cryptoflashingtool.com for complete details.
Why Choose Our Crypto Flashing Service?
Crypto Flashing is perfect for crypto enthusiasts, blockchain developers, ethical hackers, security professionals, and digital entrepreneurs looking for authenticity combined with unparalleled flexibility.
Our Crypto Flashing Features:
Instant Blockchain Verification: Transactions appear completely authentic, complete with real blockchain confirmations, transaction IDs, and wallet addresses.
Maximum Security & Privacy: Fully compatible with VPNs, TOR, and proxy servers, ensuring absolute anonymity and protection.
Easy-to-Use Software: Designed for Windows, our intuitive platform suits both beginners and experts, with detailed, step-by-step instructions provided.
Customizable Flash Durations: Control your transaction lifespan precisely, from 60 to 360 days.
Universal Wallet Compatibility: Instantly flash BTC, ETH, and USDT tokens to SegWit, Legacy, or BCH32 wallets.
Spendable on Top Exchanges: Flash coins seamlessly accepted on leading exchanges like Kraken and Huobi.
Proven Track Record:
- Over 79 Billion flash transactions completed.
- 3000+ satisfied customers worldwide.
- 42 active blockchain nodes for fast, reliable transactions.
Simple Step-by-Step Flashing Process:
Step : Enter Transaction Details
- Choose coin (BTC, ETH, USDT: TRC-20, ERC-20, BEP-20)
- Specify amount & flash duration
- Provide wallet address (validated automatically)
Step : Complete Payment & Verification
- Pay using the cryptocurrency you wish to flash
- Scan the QR code or paste the payment address
- Upload payment proof (transaction hash & screenshot)
Step : Initiate Flash Transaction
- Our technology simulates blockchain confirmations instantly
- Flash transaction appears authentic within seconds
Step : Verify & Spend Immediately
- Access your flashed crypto instantly
- Easily verify transactions via provided blockchain explorer links
Why Our Technology is Trusted:
- Race/Finney Attack Logic: Creates realistic blockchain headers.
- Private iNode Cluster: Guarantees fast synchronization and reliable transactions.
- Live Timer System: Ensures fresh wallet addresses and transaction legitimacy.
- Genuine Blockchain TX IDs: Authentic transaction IDs included with every flash
Frequently Asked Questions:
- Is flashing secure?
Yes, encrypted with full VPN/proxy support. - Can I flash from multiple devices?
Yes, up to 5 Windows PCs per license. - Are chargebacks possible?
No, flash transactions are irreversible. - How long are flash coins spendable?
From 60–360 days, based on your chosen plan. - Verification after expiry?
Transactions can’t be verified after the expiry.
Support available?
Yes, 24/7 support via Telegram & WhatsApp.
Transparent, Reliable & Highly Reviewed:
CryptoFlashingTool.com operates independently, providing unmatched transparency and reliability. Check out our glowing reviews on ScamAdvisor and leading crypto forums!
Get in Touch Now:
WhatsApp: +1 770 666 2531
Telegram: @cryptoflashingtool
Ready to Start?
Experience the smartest, safest, and most powerful crypto flashing solution on the market today!
CryptoFlashingTool.com — Flash Crypto Like a Pro.
-
 @ 9be6a199:6e133301
2025-05-20 12:24:02
@ 9be6a199:6e133301
2025-05-20 12:24:02test
-
 @ 23b0e2f8:d8af76fc
2025-01-08 18:17:52
@ 23b0e2f8:d8af76fc
2025-01-08 18:17:52Necessário
- Um Android que você não use mais (a câmera deve estar funcionando).
- Um cartão microSD (opcional, usado apenas uma vez).
- Um dispositivo para acompanhar seus fundos (provavelmente você já tem um).
Algumas coisas que você precisa saber
- O dispositivo servirá como um assinador. Qualquer movimentação só será efetuada após ser assinada por ele.
- O cartão microSD será usado para transferir o APK do Electrum e garantir que o aparelho não terá contato com outras fontes de dados externas após sua formatação. Contudo, é possível usar um cabo USB para o mesmo propósito.
- A ideia é deixar sua chave privada em um dispositivo offline, que ficará desligado em 99% do tempo. Você poderá acompanhar seus fundos em outro dispositivo conectado à internet, como seu celular ou computador pessoal.
O tutorial será dividido em dois módulos:
- Módulo 1 - Criando uma carteira fria/assinador.
- Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.
No final, teremos:
- Uma carteira fria que também servirá como assinador.
- Um dispositivo para acompanhar os fundos da carteira.

Módulo 1 - Criando uma carteira fria/assinador
-
Baixe o APK do Electrum na aba de downloads em https://electrum.org/. Fique à vontade para verificar as assinaturas do software, garantindo sua autenticidade.
-
Formate o cartão microSD e coloque o APK do Electrum nele. Caso não tenha um cartão microSD, pule este passo.

- Retire os chips e acessórios do aparelho que será usado como assinador, formate-o e aguarde a inicialização.

- Durante a inicialização, pule a etapa de conexão ao Wi-Fi e rejeite todas as solicitações de conexão. Após isso, você pode desinstalar aplicativos desnecessários, pois precisará apenas do Electrum. Certifique-se de que Wi-Fi, Bluetooth e dados móveis estejam desligados. Você também pode ativar o modo avião.\ (Curiosidade: algumas pessoas optam por abrir o aparelho e danificar a antena do Wi-Fi/Bluetooth, impossibilitando essas funcionalidades.)

- Insira o cartão microSD com o APK do Electrum no dispositivo e instale-o. Será necessário permitir instalações de fontes não oficiais.

- No Electrum, crie uma carteira padrão e gere suas palavras-chave (seed). Anote-as em um local seguro. Caso algo aconteça com seu assinador, essas palavras permitirão o acesso aos seus fundos novamente. (Aqui entra seu método pessoal de backup.)

Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.
-
Criar uma carteira somente leitura em outro dispositivo, como seu celular ou computador pessoal, é uma etapa bastante simples. Para este tutorial, usaremos outro smartphone Android com Electrum. Instale o Electrum a partir da aba de downloads em https://electrum.org/ ou da própria Play Store. (ATENÇÃO: O Electrum não existe oficialmente para iPhone. Desconfie se encontrar algum.)
-
Após instalar o Electrum, crie uma carteira padrão, mas desta vez escolha a opção Usar uma chave mestra.

- Agora, no assinador que criamos no primeiro módulo, exporte sua chave pública: vá em Carteira > Detalhes da carteira > Compartilhar chave mestra pública.

-
Escaneie o QR gerado da chave pública com o dispositivo de consulta. Assim, ele poderá acompanhar seus fundos, mas sem permissão para movimentá-los.
-
Para receber fundos, envie Bitcoin para um dos endereços gerados pela sua carteira: Carteira > Addresses/Coins.
-
Para movimentar fundos, crie uma transação no dispositivo de consulta. Como ele não possui a chave privada, será necessário assiná-la com o dispositivo assinador.

- No assinador, escaneie a transação não assinada, confirme os detalhes, assine e compartilhe. Será gerado outro QR, desta vez com a transação já assinada.

- No dispositivo de consulta, escaneie o QR da transação assinada e transmita-a para a rede.
Conclusão
Pontos positivos do setup:
- Simplicidade: Basta um dispositivo Android antigo.
- Flexibilidade: Funciona como uma ótima carteira fria, ideal para holders.
Pontos negativos do setup:
- Padronização: Não utiliza seeds no padrão BIP-39, você sempre precisará usar o electrum.
- Interface: A aparência do Electrum pode parecer antiquada para alguns usuários.
Nesse ponto, temos uma carteira fria que também serve para assinar transações. O fluxo de assinar uma transação se torna: Gerar uma transação não assinada > Escanear o QR da transação não assinada > Conferir e assinar essa transação com o assinador > Gerar QR da transação assinada > Escanear a transação assinada com qualquer outro dispositivo que possa transmiti-la para a rede.
Como alguns devem saber, uma transação assinada de Bitcoin é praticamente impossível de ser fraudada. Em um cenário catastrófico, você pode mesmo que sem internet, repassar essa transação assinada para alguém que tenha acesso à rede por qualquer meio de comunicação. Mesmo que não queiramos que isso aconteça um dia, esse setup acaba por tornar essa prática possível.
-
 @ 1bda7e1f:bb97c4d9
2025-01-02 05:19:08
@ 1bda7e1f:bb97c4d9
2025-01-02 05:19:08Tldr
- Nostr is an open and interoperable protocol
- You can integrate it with workflow automation tools to augment your experience
- n8n is a great low/no-code workflow automation tool which you can host yourself
- Nostrobots allows you to integrate Nostr into n8n
- In this blog I create some workflow automations for Nostr
- A simple form to delegate posting notes
- Push notifications for mentions on multiple accounts
- Push notifications for your favourite accounts when they post a note
- All workflows are provided as open source with MIT license for you to use
Inter-op All The Things
Nostr is a new open social protocol for the internet. This open nature exciting because of the opportunities for interoperability with other technologies. In Using NFC Cards with Nostr I explored the
nostr:URI to launch Nostr clients from a card tap.The interoperability of Nostr doesn't stop there. The internet has many super-powers, and Nostr is open to all of them. Simply, there's no one to stop it. There is no one in charge, there are no permissioned APIs, and there are no risks of being de-platformed. If you can imagine technologies that would work well with Nostr, then any and all of them can ride on or alongside Nostr rails.
My mental model for why this is special is Google Wave ~2010. Google Wave was to be the next big platform. Lars was running it and had a big track record from Maps. I was excited for it. Then, Google pulled the plug. And, immediately all the time and capital invested in understanding and building on the platform was wasted.
This cannot happen to Nostr, as there is no one to pull the plug, and maybe even no plug to pull.
So long as users demand Nostr, Nostr will exist, and that is a pretty strong guarantee. It makes it worthwhile to invest in bringing Nostr into our other applications.
All we need are simple ways to plug things together.
Nostr and Workflow Automation
Workflow automation is about helping people to streamline their work. As a user, the most common way I achieve this is by connecting disparate systems together. By setting up one system to trigger another or to move data between systems, I can solve for many different problems and become way more effective.
n8n for workflow automation
Many workflow automation tools exist. My favourite is n8n. n8n is a low/no-code workflow automation platform which allows you to build all kinds of workflows. You can use it for free, you can self-host it, it has a user-friendly UI and useful API. Vs Zapier it can be far more elaborate. Vs Make.com I find it to be more intuitive in how it abstracts away the right parts of the code, but still allows you to code when you need to.
Most importantly you can plug anything into n8n: You have built-in nodes for specific applications. HTTP nodes for any other API-based service. And community nodes built by individual community members for any other purpose you can imagine.
Eating my own dogfood
It's very clear to me that there is a big design space here just demanding to be explored. If you could integrate Nostr with anything, what would you do?
In my view the best way for anyone to start anything is by solving their own problem first (aka "scratching your own itch" and "eating your own dogfood"). As I get deeper into Nostr I find myself controlling multiple Npubs – to date I have a personal Npub, a brand Npub for a community I am helping, an AI assistant Npub, and various testing Npubs. I need ways to delegate access to those Npubs without handing over the keys, ways to know if they're mentioned, and ways to know if they're posting.
I can build workflows with n8n to solve these issues for myself to start with, and keep expanding from there as new needs come up.
Running n8n with Nostrobots
I am mostly non-technical with a very helpful AI. To set up n8n to work with Nostr and operate these workflows should be possible for anyone with basic technology skills.
- I have a cheap VPS which currently runs my HAVEN Nostr Relay and Albyhub Lightning Node in Docker containers,
- My objective was to set up n8n to run alongside these in a separate Docker container on the same server, install the required nodes, and then build and host my workflows.
Installing n8n
Self-hosting n8n could not be easier. I followed n8n's Docker-Compose installation docs–
- Install Docker and Docker-Compose if you haven't already,
- Create your
docker-compose.ymland.envfiles from the docs, - Create your data folder
sudo docker volume create n8n_data, - Start your container with
sudo docker compose up -d, - Your n8n instance should be online at port
5678.
n8n is free to self-host but does require a license. Enter your credentials into n8n to get your free license key. You should now have access to the Workflow dashboard and can create and host any kind of workflows from there.
Installing Nostrobots
To integrate n8n nicely with Nostr, I used the Nostrobots community node by Ocknamo.
In n8n parlance a "node" enables certain functionality as a step in a workflow e.g. a "set" node sets a variable, a "send email" node sends an email. n8n comes with all kinds of "official" nodes installed by default, and Nostr is not amongst them. However, n8n also comes with a framework for community members to create their own "community" nodes, which is where Nostrobots comes in.
You can only use a community node in a self-hosted n8n instance (which is what you have if you are running in Docker on your own server, but this limitation does prevent you from using n8n's own hosted alternative).
To install a community node, see n8n community node docs. From your workflow dashboard–
- Click the "..." in the bottom left corner beside your username, and click "settings",
- Cilck "community nodes" left sidebar,
- Click "Install",
- Enter the "npm Package Name" which is
n8n-nodes-nostrobots, - Accept the risks and click "Install",
- Nostrobots is now added to your n8n instance.
Using Nostrobots
Nostrobots gives you nodes to help you build Nostr-integrated workflows–
- Nostr Write – for posting Notes to the Nostr network,
- Nostr Read – for reading Notes from the Nostr network, and
- Nostr Utils – for performing certain conversions you may need (e.g. from bech32 to hex).
Nostrobots has good documentation on each node which focuses on simple use cases.
Each node has a "convenience mode" by default. For example, the "Read" Node by default will fetch Kind 1 notes by a simple filter, in Nostrobots parlance a "Strategy". For example, with Strategy set to "Mention" the node will accept a pubkey and fetch all Kind 1 notes that Mention the pubkey within a time period. This is very good for quick use.
What wasn't clear to me initially (until Ocknamo helped me out) is that advanced use cases are also possible.
Each node also has an advanced mode. For example, the "Read" Node can have "Strategy" set to "RawFilter(advanced)". Now the node will accept json (anything you like that complies with NIP-01). You can use this to query Notes (Kind 1) as above, and also Profiles (Kind 0), Follow Lists (Kind 3), Reactions (Kind 7), Zaps (Kind 9734/9735), and anything else you can think of.
Creating and adding workflows
With n8n and Nostrobots installed, you can now create or add any kind of Nostr Workflow Automation.
- Click "Add workflow" to go to the workflow builder screen,
- If you would like to build your own workflow, you can start with adding any node. Click "+" and see what is available. Type "Nostr" to explore the Nostrobots nodes you have added,
- If you would like to add workflows that someone else has built, click "..." in the top right. Then click "import from URL" and paste in the URL of any workflow you would like to use (including the ones I share later in this article).
Nostr Workflow Automations
It's time to build some things!
A simple form to post a note to Nostr
I started very simply. I needed to delegate the ability to post to Npubs that I own in order that a (future) team can test things for me. I don't want to worry about managing or training those people on how to use keys, and I want to revoke access easily.
I needed a basic form with credentials that posted a Note.
For this I can use a very simple workflow–
- A n8n Form node – Creates a form for users to enter the note they wish to post. Allows for the form to be protected by a username and password. This node is the workflow "trigger" so that the workflow runs each time the form is submitted.
- A Set node – Allows me to set some variables, in this case I set the relays that I intend to use. I typically add a Set node immediately following the trigger node, and put all the variables I need in this. It helps to make the workflows easier to update and maintain.
- A Nostr Write node (from Nostrobots) – Writes a Kind-1 note to the Nostr network. It accepts Nostr credentials, the output of the Form node, and the relays from the Set node, and posts the Note to those relays.
Once the workflow is built, you can test it with the testing form URL, and set it to "Active" to use the production form URL. That's it. You can now give posting access to anyone for any Npub. To revoke access, simply change the credentials or set to workflow to "Inactive".
It may also be the world's simplest Nostr client.
You can find the Nostr Form to Post a Note workflow here.
Push notifications on mentions and new notes
One of the things Nostr is not very good at is push notifications. Furthermore I have some unique itches to scratch. I want–
- To make sure I never miss a note addressed to any of my Npubs – For this I want a push notification any time any Nostr user mentions any of my Npubs,
- To make sure I always see all notes from key accounts – For this I need a push notification any time any of my Npubs post any Notes to the network,
- To get these notifications on all of my devices – Not just my phone where my Nostr regular client lives, but also on each of my laptops to suit wherever I am working that day.
I needed to build a Nostr push notifications solution.
To build this workflow I had to string a few ideas together–
- Triggering the node on a schedule – Nostrobots does not include a trigger node. As every workflow starts with a trigger we needed a different method. I elected to run the workflow on a schedule of every 10-minutes. Frequent enough to see Notes while they are hot, but infrequent enough to not burden public relays or get rate-limited,
- Storing a list of Npubs in a Nostr list – I needed a way to store the list of Npubs that trigger my notifications. I initially used an array defined in the workflow, this worked fine. Then I decided to try Nostr lists (NIP-51, kind 30000). By defining my list of Npubs as a list published to Nostr I can control my list from within a Nostr client (e.g. Listr.lol or Nostrudel.ninja). Not only does this "just work", but because it's based on Nostr lists automagically Amethyst client allows me to browse that list as a Feed, and everyone I add gets notified in their Mentions,
- Using specific relays – I needed to query the right relays, including my own HAVEN relay inbox for notes addressed to me, and wss://purplepag.es for Nostr profile metadata,
- Querying Nostr events (with Nostrobots) – I needed to make use of many different Nostr queries and use quite a wide range of what Nostrobots can do–
- I read the EventID of my Kind 30000 list, to return the desired pubkeys,
- For notifications on mentions, I read all Kind 1 notes that mention that pubkey,
- For notifications on new notes, I read all Kind 1 notes published by that pubkey,
- Where there are notes, I read the Kind 0 profile metadata event of that pubkey to get the displayName of the relevant Npub,
- I transform the EventID into a Nevent to help clients find it.
- Using the Nostr URI – As I did with my NFC card article, I created a link with the
nostr:URI prefix so that my phone's native client opens the link by default, - Push notifications solution – I needed a push notifications solution. I found many with n8n integrations and chose to go with Pushover which supports all my devices, has a free trial, and is unfairly cheap with a $5-per-device perpetual license.
Once the workflow was built, lists published, and Pushover installed on my phone, I was fully set up with push notifications on Nostr. I have used these workflows for several weeks now and made various tweaks as I went. They are feeling robust and I'd welcome you to give them a go.
You can find the Nostr Push Notification If Mentioned here and If Posts a Note here.
In speaking with other Nostr users while I was building this, there are all kind of other needs for push notifications too – like on replies to a certain bookmarked note, or when a followed Npub starts streaming on zap.stream. These are all possible.
Use my workflows
I have open sourced all my workflows at my Github with MIT license and tried to write complete docs, so that you can import them into your n8n and configure them for your own use.
To import any of my workflows–
- Click on the workflow of your choice, e.g. "Nostr_Push_Notify_If_Mentioned.json",
- Click on the "raw" button to view the raw JSON, ex any Github page layout,
- Copy that URL,
- Enter that URL in the "import from URL" dialog mentioned above.
To configure them–
- Prerequisites, credentials, and variables are all stated,
- In general any variables required are entered into a Set Node that follows the trigger node,
- Pushover has some extra setup but is very straightforward and documented in the workflow.
What next?
Over my first four blogs I explored creating a good Nostr setup with Vanity Npub, Lightning Payments, Nostr Addresses at Your Domain, and Personal Nostr Relay.
Then in my latest two blogs I explored different types of interoperability with NFC cards and now n8n Workflow Automation.
Thinking ahead n8n can power any kind of interoperability between Nostr and any other legacy technology solution. On my mind as I write this:
- Further enhancements to posting and delegating solutions and forms (enhanced UI or different note kinds),
- Automated or scheduled posting (such as auto-liking everything Lyn Alden posts),
- Further enhancements to push notifications, on new and different types of events (such as notifying me when I get a new follower, on replies to certain posts, or when a user starts streaming),
- All kinds of bridges, such as bridging notes to and from Telegram, Slack, or Campfire. Or bridging RSS or other event feeds to Nostr,
- All kinds of other automation (such as BlackCoffee controlling a coffee machine),
- All kinds of AI Assistants and Agents,
In fact I have already released an open source workflow for an AI Assistant, and will share more about that in my next blog.
Please be sure to let me know if you think there's another Nostr topic you'd like to see me tackle.
GM Nostr.
-
 @ dfc7c785:4c3c6174
2025-05-20 09:55:44
@ dfc7c785:4c3c6174
2025-05-20 09:55:44![[0B745064-2D34-4A3C-8393-AD033910E6D7.jpeg]]![[0C3FA837-E1BA-497F-8D44-9EC1CD723970.jpeg]]
-
 @ 90c656ff:9383fd4e
2025-05-20 09:06:27
@ 90c656ff:9383fd4e
2025-05-20 09:06:27Since its creation in 2008, Bitcoin has been seen as a direct challenge to the traditional banking system. Developed as a decentralized alternative to fiat money, Bitcoin offers a way to store and transfer value without relying on banks, governments, or other financial institutions. This characteristic has made it a symbol of resistance against a financial system that, over time, has been marked by crises, manipulation, and restrictions imposed on citizens.
The 2008 financial crisis and the birth of Bitcoin
Bitcoin emerged in response to the 2008 financial crisis—a collapse that exposed the flaws of the global banking system. Central banks printed massive amounts of money to bail out irresponsible financial institutions, while millions of people lost their homes, savings, and jobs. In this context, Bitcoin was created as an alternative financial system, where no central authority could manipulate the economy for its own benefit.
In the first block of the Bitcoin blockchain or timechain, Satoshi Nakamoto included the following message:
“The Times 03/Jan/2009 Chancellor on brink of second bailout for banks.”
This phrase, taken from a newspaper headline of the time, symbolizes Bitcoin’s intent to offer a financial system beyond the control of banks and governments.
- Key reasons why Bitcoin resists the banking system
01 - Decentralization: Unlike money issued by central banks, Bitcoin cannot be created or controlled by any single entity. The network of users validates transactions transparently and independently.
02 - Limited Supply: While central banks can print money without limit—causing inflation and currency devaluation—Bitcoin has a fixed supply of 21 million units, making it resistant to artificial depreciation.
03 - Censorship Resistance: Banks can freeze accounts and block transactions at any time. With Bitcoin, anyone can send and receive funds without needing permission from third parties.
04 - Self-Custody: Instead of entrusting funds to a bank, Bitcoin users can store their own coins without the risk of account freezes or bank failures.
- Conflict between banks and Bitcoin
01 - Media Attacks: Large financial institutions often label Bitcoin as risky, volatile, or useless, attempting to discourage its adoption.
02 - Regulation and Crackdowns: Some governments, influenced by the banking sector, have implemented restrictions on Bitcoin usage, making it harder to buy and sell.
03 - Creation of Centralized Alternatives: Many central banks are developing digital currencies (CBDCs) that maintain control over digital money but do not offer Bitcoin’s freedom and decentralization.
In summary, Bitcoin is not just a digital currency—it is a movement of resistance against a financial system that has repeatedly failed to protect ordinary citizens. By offering a decentralized, transparent, and censorship-resistant alternative, Bitcoin represents financial freedom and challenges the banking monopoly over money. As long as the traditional banking system continues to impose restrictions and control the flow of capital, Bitcoin will remain a symbol of independence and financial sovereignty.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ bd4ae3e6:1dfb81f5
2025-05-20 08:46:08
@ bd4ae3e6:1dfb81f5
2025-05-20 08:46:08 -
 @ bd4ae3e6:1dfb81f5
2025-05-20 08:46:06
@ bd4ae3e6:1dfb81f5
2025-05-20 08:46:06 -
 @ f9cf4e94:96abc355
2024-12-31 20:18:59
@ f9cf4e94:96abc355
2024-12-31 20:18:59Scuttlebutt foi iniciado em maio de 2014 por Dominic Tarr ( dominictarr ) como uma rede social alternativa off-line, primeiro para convidados, que permite aos usuários obter controle total de seus dados e privacidade. Secure Scuttlebutt (ssb) foi lançado pouco depois, o que coloca a privacidade em primeiro plano com mais recursos de criptografia.
Se você está se perguntando de onde diabos veio o nome Scuttlebutt:
Este termo do século 19 para uma fofoca vem do Scuttlebutt náutico: “um barril de água mantido no convés, com um buraco para uma xícara”. A gíria náutica vai desde o hábito dos marinheiros de se reunir pelo boato até a fofoca, semelhante à fofoca do bebedouro.

Marinheiros se reunindo em torno da rixa. ( fonte )
Dominic descobriu o termo boato em um artigo de pesquisa que leu.
Em sistemas distribuídos, fofocar é um processo de retransmissão de mensagens ponto a ponto; as mensagens são disseminadas de forma análoga ao “boca a boca”.
Secure Scuttlebutt é um banco de dados de feeds imutáveis apenas para acréscimos, otimizado para replicação eficiente para protocolos ponto a ponto. Cada usuário tem um log imutável somente para acréscimos no qual eles podem gravar. Eles gravam no log assinando mensagens com sua chave privada. Pense em um feed de usuário como seu próprio diário de bordo, como um diário de bordo (ou diário do capitão para os fãs de Star Trek), onde eles são os únicos autorizados a escrever nele, mas têm a capacidade de permitir que outros amigos ou colegas leiam ao seu diário de bordo, se assim o desejarem.
Cada mensagem possui um número de sequência e a mensagem também deve fazer referência à mensagem anterior por seu ID. O ID é um hash da mensagem e da assinatura. A estrutura de dados é semelhante à de uma lista vinculada. É essencialmente um log somente de acréscimo de JSON assinado. Cada item adicionado a um log do usuário é chamado de mensagem.
Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações. Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.

Estrutura de alto nível de um feed
Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar. Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência.
Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub.
Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.
Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de Pubs públicos em que todos podem participar . Explicaremos como ingressar em um posteriormente neste guia. Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais. Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.

Perspectivas dos participantes
Scuttlebot
O software Pub é conhecido como servidor Scuttlebutt (servidor ssb ), mas também é conhecido como “Scuttlebot” e
sbotna linha de comando. O servidor SSB adiciona comportamento de rede ao banco de dados Scuttlebutt (SSB). Estaremos usando o Scuttlebot ao longo deste tutorial.Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações. Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.

Estrutura de alto nível de um feed
Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar. Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência.
Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub.
Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.
Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de Pubs públicos em que todos podem participar . Explicaremos como ingressar em um posteriormente neste guia. Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais. Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.


Perspectivas dos participantes
Pubs - Hubs
Pubs públicos
| Pub Name | Operator | Invite Code | | ------------------------------------------------------------ | ------------------------------------------------------------ | ------------------------------------------------------------ | |
scuttle.us| @Ryan |scuttle.us:8008:@WqcuCOIpLtXFRw/9vOAQJti8avTZ9vxT9rKrPo8qG6o=.ed25519~/ZUi9Chpl0g1kuWSrmehq2EwMQeV0Pd+8xw8XhWuhLE=| | pub1.upsocial.com | @freedomrules |pub1.upsocial.com:8008:@gjlNF5Cyw3OKZxEoEpsVhT5Xv3HZutVfKBppmu42MkI=.ed25519~lMd6f4nnmBZEZSavAl4uahl+feajLUGqu8s2qdoTLi8=| | Monero Pub | @Denis |xmr-pub.net:8008:@5hTpvduvbDyMLN2IdzDKa7nx7PSem9co3RsOmZoyyCM=.ed25519~vQU+r2HUd6JxPENSinUWdfqrJLlOqXiCbzHoML9iVN4=| | FreeSocial | @Jarland |pub.freesocial.co:8008:@ofYKOy2p9wsaxV73GqgOyh6C6nRGFM5FyciQyxwBd6A=.ed25519~ye9Z808S3KPQsV0MWr1HL0/Sh8boSEwW+ZK+8x85u9w=| |ssb.vpn.net.br| @coffeverton |ssb.vpn.net.br:8008:@ze8nZPcf4sbdULvknEFOCbVZtdp7VRsB95nhNw6/2YQ=.ed25519~D0blTolH3YoTwSAkY5xhNw8jAOjgoNXL/+8ZClzr0io=| | gossip.noisebridge.info | Noisebridge Hackerspace @james.network |gossip.noisebridge.info:8008:@2NANnQVdsoqk0XPiJG2oMZqaEpTeoGrxOHJkLIqs7eY=.ed25519~JWTC6+rPYPW5b5zCion0gqjcJs35h6JKpUrQoAKWgJ4=|Pubs privados
Você precisará entrar em contato com os proprietários desses bares para receber um convite.
| Pub Name | Operator | Contact | | --------------------------------------------- | ------------------------------------------------------------ | ----------------------------------------------- | |
many.butt.nz| @dinosaur | mikey@enspiral.com | |one.butt.nz| @dinosaur | mikey@enspiral.com | |ssb.mikey.nz| @dinosaur | mikey@enspiral.com | | ssb.celehner.com | @cel | cel@celehner.com |Pubs muito grandes
Aviso: embora tecnicamente funcione usar um convite para esses pubs, você provavelmente se divertirá se o fizer devido ao seu tamanho (muitas coisas para baixar, risco para bots / spammers / idiotas)
| Pub Name | Operator | Invite Code | | --------------------------------------- | ----------------------------------------------- | ------------------------------------------------------------ | |
scuttlebutt.de| SolSoCoG |scuttlebutt.de:8008:@yeh/GKxlfhlYXSdgU7CRLxm58GC42za3tDuC4NJld/k=.ed25519~iyaCpZ0co863K9aF+b7j8BnnHfwY65dGeX6Dh2nXs3c=| |Lohn's Pub| @lohn |p.lohn.in:8018:@LohnKVll9HdLI3AndEc4zwGtfdF/J7xC7PW9B/JpI4U=.ed25519~z3m4ttJdI4InHkCtchxTu26kKqOfKk4woBb1TtPeA/s=| | Scuttle Space | @guil-dot | Visit scuttle.space | |SSB PeerNet US-East| timjrobinson |us-east.ssbpeer.net:8008:@sTO03jpVivj65BEAJMhlwtHXsWdLd9fLwyKAT1qAkc0=.ed25519~sXFc5taUA7dpGTJITZVDCRy2A9jmkVttsr107+ufInU=| | Hermies | s | net:hermies.club:8008~shs:uMYDVPuEKftL4SzpRGVyQxLdyPkOiX7njit7+qT/7IQ=:SSB+Room+PSK3TLYC2T86EHQCUHBUHASCASE18JBV24= |GUI - Interface Gráfica do Utilizador(Usuário)
Patchwork - Uma GUI SSB (Descontinuado)
Patchwork é o aplicativo de mensagens e compartilhamento descentralizado construído em cima do SSB . O protocolo scuttlebutt em si não mantém um conjunto de feeds nos quais um usuário está interessado, então um cliente é necessário para manter uma lista de feeds de pares em que seu respectivo usuário está interessado e seguindo.

Fonte: scuttlebutt.nz
Quando você instala e executa o Patchwork, você só pode ver e se comunicar com seus pares em sua rede local. Para acessar fora de sua LAN, você precisa se conectar a um Pub. Um pub é apenas para convidados e eles retransmitem mensagens entre você e seus pares fora de sua LAN e entre outros Pubs.
Lembre-se de que você precisa seguir alguém para receber mensagens dessa pessoa. Isso reduz o envio de mensagens de spam para os usuários. Os usuários só veem as respostas das pessoas que seguem. Os dados são sincronizados no disco para funcionar offline, mas podem ser sincronizados diretamente com os pares na sua LAN por wi-fi ou bluetooth.
Patchbay - Uma GUI Alternativa
Patchbay é um cliente de fofoca projetado para ser fácil de modificar e estender. Ele usa o mesmo banco de dados que Patchwork e Patchfoo , então você pode facilmente dar uma volta com sua identidade existente.

Planetary - GUI para IOS

Planetary é um app com pubs pré-carregados para facilitar integração.
Manyverse - GUI para Android

Manyverse é um aplicativo de rede social com recursos que você esperaria: posts, curtidas, perfis, mensagens privadas, etc. Mas não está sendo executado na nuvem de propriedade de uma empresa, em vez disso, as postagens de seus amigos e todos os seus dados sociais vivem inteiramente em seu telefone .
Fontes
-
https://scuttlebot.io/
-
https://decentralized-id.com/decentralized-web/scuttlebot/#plugins
-
https://medium.com/@miguelmota/getting-started-with-secure-scuttlebut-e6b7d4c5ecfd
-
Secure Scuttlebutt : um protocolo de banco de dados global.
-
-
 @ 98912a0b:c1f46ab6
2025-05-20 07:15:49
@ 98912a0b:c1f46ab6
2025-05-20 07:15:49Jo, blomster kommer i alle farger og fasonger. Her har du to eksempler:


-
 @ 98912a0b:c1f46ab6
2025-05-20 07:15:47
@ 98912a0b:c1f46ab6
2025-05-20 07:15:47Skjønner du? Bare tekst.
-
 @ fb3d3798:371f711a
2025-05-20 07:13:37
@ fb3d3798:371f711a
2025-05-20 07:13:37Jo, blomster kommer i alle farger og fasonger. Her har du to eksempler:


-
 @ fb3d3798:371f711a
2025-05-20 07:13:35
@ fb3d3798:371f711a
2025-05-20 07:13:35Skjønner du? Bare tekst.