-
 @ 0e29efc2:ff142af2
2025-05-07 15:09:46
@ 0e29efc2:ff142af2
2025-05-07 15:09:46Table of Contents
- Intro
- Important Terminology
- Getting Started
- Where do I buy bitcoin?
- Okay, I bought some bitcoin-now what?
- Less than 0.01 BTC
- More than 0.01 BTC and less than 0.1 BTC
- More than 0.1 BTC
- How Bitcoin Works
- Skepticism
- Someone will hack it
- The government will try to stop it
- It’s not backed by anything
- Conclusion
Intro
Maybe you saw an article in Forbes, a news segment about MicroStrategy (MSTR), or you glanced at the bitcoin price chart; whatever the spark, your curiosity led you here. Enough friends and relatives keep asking me about bitcoin that I finally organized my thoughts into a single reference. This is not a comprehensive guide—it assumes you trust me as a heuristic.
Important Terminology
Sat (satoshi) – the smallest unit of bitcoin. One bitcoin (₿) equals 100 000 000 sats.
Getting Started
Where do I buy bitcoin?
I use River because it publishes proof‑of‑reserves, supports the Lightning Network, and pays interest on idle USD balances (currently 3.8 %).
Okay, I bought some bitcoin-now what?
Withdraw it immediately. Centralized exchanges can and do fail. Your next step depends on how much bitcoin you hold.
If at any point you're struggling, please reach out to me.
Less than 0.01 BTC
- On your phone open Safari (iOS) or Chrome (Android).
- Paste
https://wallet.cashu.me?mint=https://mint.westernbtc.com. Confirm the prompt that asks whether you trusthttps://mint.westernbtc.com. I run this mint so beginners can skip the gnarly parts. - Complete setup.
- Tap Receive → LIGHTNING → enter amount → COPY.
- In River choose Send → Send to a Bitcoin wallet, paste the invoice, verify, and send.
- Return to the wallet; your sats should appear.

More than 0.01 BTC and less than 0.1 BTC
It's time for cold storage. Cold storage means a dedicated signing device not connected to the internet. Think of it like keys to a house. If you have the keys (your cold storage signing device), you can get into your house (the bitcoin). I recommend and use the COLDCARD Q or COLDCARD MK4 from COLDCARD. See this thorough walkthrough.
The creator nostr:npub1rxysxnjkhrmqd3ey73dp9n5y5yvyzcs64acc9g0k2epcpwwyya4spvhnp8 makes reliable content.
More than 0.1 BTC
The next security upgrade involves something called multisig. It requires the use of multiple devices instead of one. Think of those nuclear launch silos in movies where two keys need to be turned in order to launch the missile. One person can't reach both keys, so you need two people. Like the two keys needing to be turned, we need a certain number of keys (signing devices) to be used.

This offers a number of benefits. Say you have a 2-of-3 multisig setup. You would need two of the three keys to move the bitcoin. If you were to lose one, you could use the two others to move it instead. Many choose to geographically distribute the keys; choosing to keep one at a friend’s house or with a bank.
The previous video I linked covers multisig as well. Again, please reach out to me if you need help.
How Bitcoin Works
I'm going to paint a scene portraying the basics of how bitcoin works. Picture a race that's supposed to take 10 minutes to run start-to-finish, and there's a crowd of people spectating. When the fastest runner crosses the finish line, they're awarded 50 bitcoin. Everyone in the crowd recognizes who won, and writes it down on their own scoreboard. Then, the next race begins.
Now, let's say more racers who've had special training join. They start winning consistently because of it, and now the race only lasts about 9 minutes. There's a special rule everyone in the crowd agreed to, that they can make the race harder to ensure it's around 10 minutes long. So they make the race harder to counteract the faster runners.

With this in mind, let's get to the skepticism you might have.
Skepticism
Someone will hack it
Think of bitcoin as the people in the crowd. If someone tries to cheat and writes on their scoreboard that they have a billion bitcoin, their scoreboard is going to look different than everybody else’s. The other people in the crowd will cross-reference with each other and decide to ignore that person who cheated.
The government will try to stop it
Again, think of the crowd. In reality, the "crowd participants" are scattered all around the world. You might be able to stop many of them, but it would be almost impossible to stop everyone. Imagine people are watching the race on TV, can you find everyone who's spectating? Ironically, attempted bans often increase interest.
It’s not backed by anything.
Think of the runners. The runners are bitcoin miners. They have to expend real energy to participate in the race. The more bitcoin miners, the more secure the network. In summary, it's backed by electricity and work.
Conclusion
There are too many topics to cover in one article. I haven't even touched on the history of money, what money is, scarcity, etc. The best way to learn is to research the topics you're interested in for yourself. It took months of deep diving before I was sold on bitcoin, and I had many touch points before that.
Once you see it though, you can't unsee it.
-
 @ 502ab02a:a2860397
2025-05-08 01:18:46
@ 502ab02a:a2860397
2025-05-08 01:18:46เฮียไม่แน่ใจว่าโลกยุคนี้มันเปลี่ยนไป หรือแค่เล่ห์กลมันแนบเนียนขึ้น แต่ที่แน่ ๆ คือ “อาหารไม่ใช่อาหารอีกต่อไป” มันกลายเป็นสินค้าในพอร์ตการลงทุน มันกลายเป็นเครื่องมือสร้างภาพลักษณ์ และในบางมุมที่คนไม่อยากมอง...มันคือเครื่องมือควบคุมมวลชน
ทุกอย่างเริ่มจากแนวคิดที่ดูดี “เราต้องผลิตอาหารให้พอเลี้ยงคน 8,000 ล้านคน” จากนั้นบริษัทเทคโนโลยีเริ่มกระโดดเข้ามา แทนที่จะให้เกษตรกรปลูกผักเลี้ยงวัว เรากลับได้เห็นบริษัทวิเคราะห์ดีเอ็นเอของจุลินทรีย์ แล้วขายโปรตีนจากถังหมัก แทนที่จะสนับสนุนอาหารพื้นบ้าน กลับอัดเงินให้สตาร์ทอัพทำเบอร์เกอร์ที่ไม่มีเนื้อจริงแม้แต่เส้นใยเดียว
เบื้องหลังมันมี “ทุน” และทุนเหล่านี้ไม่ใช่แค่ผู้ผลิตอาหาร แต่พ่วงไปถึงบริษัทยา บริษัทวัคซีน บริษัทเทคโนโลยี บางเจ้ามีทั้งบริษัทยา + ธุรกิจฟาร์มแมลง + บริษัทลงทุนในบริษัทวิจัยพันธุกรรม แปลว่า...คนที่ขายยาให้เฮียเวลาเฮียป่วย อาจเป็นคนเดียวกับที่ขาย "อาหารที่ทำให้เฮียป่วย" ตั้งแต่แรก ตลกร้ายไหมหล่ะ หึหึหึ
เคยมีใครสังเกตไหม ว่าองค์การระดับโลกบางองค์กรที่ส่งเสริม "เนื้อทางเลือก" และ "อาหารยั่งยืน" ได้รับเงินบริจาคหรืออยู่ภายใต้บอร์ดของบริษัทผลิตอาหารอุตสาหกรรมเจ้าใหญ่ไหมนะ แล้วคำว่า “วิทยาศาสตร์รองรับ” ที่ติดบนฉลากสวย ๆ เฮียไม่รู้หรอกว่าใครเป็นคนตีความ แต่ที่รู้แน่ ๆ คือ บทวิจัยจำนวนไม่น้อย มาจากทุนวิจัยที่สนับสนุนโดยอุตสาหกรรมอาหารเอง ดั่งเช่นที่เราเรียนรู้กันมาจากประวัติศาสตร์แล้ว
มีคนเคยพูดไว้ว่า “เราควบคุมคนด้วยอาหารง่ายกว่าด้วยอาวุธ” และเฮียเริ่มเชื่อขึ้นเรื่อย ๆ เพราะถ้าบริษัทใดบริษัทหนึ่ง ควบคุมได้ทั้งอาหาร ยา ข้อมูลสุขภาพ และการวิจัย นั่นหมายความว่า เขาไม่ได้ขายของให้เฮีย แต่เขากำหนดว่าเฮียควร “อยากกินอะไร” และ “รู้สึกผิดกับอะไร”
เหมือนที่ให้ลองจินตนาการเล่น ๆ เมื่อวาน สมมติเฮียไปร้านข้าวมันไก่ปากซอยแบบดั้งเดิม สั่งไก่ต้มไม่เอาข้าวมากิน แล้วแอปสุขภาพขึ้นข้อความเตือนว่า “ไขมันสูง ส่งผลต่อคะแนนสุขภาพคุณ” แต่ถ้าเฮียสั่งข้าวกล่องสำเร็จรูปอัจฉริยะจากโปรตีนที่หมักจากจุลินทรีย์ GMO ระบบจะบอกว่า “คุณกำลังช่วยลดโลกร้อน” แล้วเพิ่มคะแนนสุขภาพให้เราไปเป็นส่วนลดครั้งต่อไป
ใครนิยามคำว่า “ดี” ให้เฮีย?
เบื้องหลังอาหารจึงไม่ใช่แค่โรงงาน แต่มันคือโครงข่ายที่พัวพันตั้งแต่ห้องแล็บ ห้องบอร์ด ไปจนถึงห้องครัวในบ้านเรา แล้วถ้าเราไม่ตั้งคำถาม เฮียกลัวว่าเราจะไม่ได้กินในสิ่งที่ร่างกายต้องการ แต่กินในสิ่งที่ “ระบบ” ต้องการให้เรากิน
ขอบคุณล่วงหน้าที่มองว่าสิ่งนี้คือการ แพนิคไปเอง ขอให้มีสุขสวัสดิ์
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 6d8e2a24:5faaca4c
2025-05-07 19:15:55
@ 6d8e2a24:5faaca4c
2025-05-07 19:15:55Decentralized social media platforms like Yakinhonne is gaining popularity as alternatives to traditional networks like Facebook and Twitter. But here’s the big question: Can you actually make money from them?
Unlike traditional social media with the likes of Facebook, Twitter, Instagram, WhatsApp etc. Yakihonne runs on blockchain tech, meaning:
✅ You own your content (no shadow banning or sudden account bans).
✅ No creepy ads tracking your every move.
✅ Real monetization no waiting for a partner program approval.Therefore the short answer? Yes! But it’s different from how monetization works on mainstream platforms. Let’s break it down in simple terms.

- How Decentralized Social Media Works
Unlike Facebook or Instagram (which are owned by corporations), decentralized platforms run on blockchain or peer to peer networks. This means:
✅ No central control (no Zuckerberg making the rules).
✅ Users own their data (no creepy ads tracking you).
✅ More freedom (fewer bans and censorship).
But since these platforms don’t rely on ads, how do creators and users earn money?
2. Ways to earn on Yakinhonne Decentralized Social Media Platform.
A. Rewards & Tipping ✅ Users can tip you in crypto SAT (Satoshi, which is a native of Bitcoin) for great content.
✅ Earn tokens for engagement (likes, shares, etc.).
Example: Post a viral thread on Yakinhonne and followers might send you $SAT Tokens as appreciation.
B. Paid Subscriptions & Exclusive Content
✅ Platforms like Yakinhonne allow paid memberships.
✅ Offer premium posts (Flash news or post), private chats, or early access to supporters.Example: A writer post a paid article making it stand out, attracting more engagement which in returns earns more SAT.
C. Decentralized Ads (But Better)
✅Instead of intrusive ads, users opt-in to promotions.
✅ Creators get paid directly for promoting products (no middleman).Example: A tech reviewer gets paid in crypto for sharing a decentralized VPN service.
D. Affiliate Marketing & Sponsorships
✅ Promote products and earn commissions (like Amazon links).
✅ Partner with Web3 brands (crypto projects, tools, etc.).Conclusion:
Decentralized social media is still growing, but the monetization potential is real especially if you’re a lover of freedom, having absolute control and fairness.
As blockchain technology evolves, we might see even smarter ways to earn on these platform. So, getting in early could be a smart move!
- How Decentralized Social Media Works
Unlike Facebook or Instagram (which are owned by corporations), decentralized platforms run on blockchain or peer to peer networks. This means:
-
 @ 90c656ff:9383fd4e
2025-05-07 18:25:24
@ 90c656ff:9383fd4e
2025-05-07 18:25:24Bitcoin is known for its strong volatility, with price swings that can occur over short periods of time. This characteristic attracts both investors seeking high returns and deters those who prefer more stable assets. Bitcoin's price volatility has a significant impact on the market, influencing investment strategies, adoption, and even public perception of the digital currency.
What Causes Bitcoin's Price Volatility?
Bitcoin’s volatility is due to several factors that affect its supply and demand. Among the main reasons are:
01 - Limited supply and halving: Bitcoin has a maximum supply of 21 million units, creating scarcity. Additionally, the halving-an event that reduces the issuance of new bitcoins every four years-can drive up prices due to the reduced supply.
02 - Market speculation: Many investors buy and sell Bitcoin in pursuit of quick profits, causing large price fluctuations. Speculative movements, often driven by news and social media, can trigger abrupt changes in price.
03 - Economic events and regulation: Government decisions-such as bans or favorable regulations-directly impact the price. Statements from central banks or influential figures in the financial sector can also trigger strong market reactions.
04 - Liquidity and trading volume: The Bitcoin market is still small compared to traditional assets like gold or stocks. This means that large buy or sell orders can cause significant price swings.
- Impact on Investors and “Investors”
Bitcoin’s price volatility affects different types of investors in different ways:
01 - Short-term traders: Day traders attempt to profit from price swings. However, this strategy carries high risks and can lead to significant losses for those without market experience.
02 - Long-term investors (HODLers): Those who invest with a long-term perspective typically ignore daily price changes and focus on Bitcoin's potential appreciation over the years. Despite temporary dips, many believe the price will continue to rise due to scarcity and increasing adoption.
03 - Companies and institutions: Companies investing in Bitcoin as a store of value-like MicroStrategy and Tesla, must manage the risks of volatility. Some adopt strategies to minimize direct exposure to large fluctuations.
- How to deal with volatility
Despite the challenges, there are strategic ways to manage Bitcoin’s volatility:
01 - Portfolio diversification: Instead of investing all capital in Bitcoin, many investors diversify to reduce the impact of price fluctuations.
02 - Recurring investment: Strategies like dollar-cost averaging (recurring, fractional purchases) help smooth out volatility effects, reducing the risk of buying during a temporary high.
03 - Secure storage: Rather than leaving Bitcoin on exchanges—which can be vulnerable to hacks and market manipulation—self-custody in secure wallets protects long-term investments.
In summary, Bitcoin's volatility is one of its defining traits and influences both investor behavior and broader adoption. While it offers opportunities for large profits, it also carries considerable risk, requiring well-defined strategies to minimize losses. As Bitcoin matures and more institutional investors enter the market, volatility may decrease, making it even more attractive as a store of value.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ 40bdcc08:ad00fd2c
2025-05-06 14:24:22
@ 40bdcc08:ad00fd2c
2025-05-06 14:24:22Introduction
Bitcoin’s
OP_RETURNopcode, a mechanism for embedding small data in transactions, has ignited a significant debate within the Bitcoin community. Originally designed to support limited metadata while preserving Bitcoin’s role as a peer-to-peer electronic cash system,OP_RETURNis now at the center of proposals that could redefine Bitcoin’s identity. The immutable nature of Bitcoin’s timechain makes it an attractive platform for data storage, creating tension with those who prioritize its monetary function. This discussion, particularly around Bitcoin Core pull request #32406 (GitHub PR #32406), highlights a critical juncture for Bitcoin’s future.What is
OP_RETURN?Introduced in 2014,
OP_RETURNallows users to attach up to 80 bytes of data to a Bitcoin transaction. Unlike other transaction outputs,OP_RETURNoutputs are provably unspendable, meaning they don’t burden the Unspent Transaction Output (UTXO) set—a critical database for Bitcoin nodes. This feature was a compromise to provide a standardized, less harmful way to include metadata, addressing earlier practices that embedded data in ways that bloated the UTXO set. The 80-byte limit and restriction to oneOP_RETURNoutput per transaction are part of Bitcoin Core’s standardness rules, which guide transaction relay and mining but are not enforced by the network’s consensus rules (Bitcoin Stack Exchange).Standardness vs. Consensus Rules
Standardness rules are Bitcoin Core’s default policies for relaying and mining transactions. They differ from consensus rules, which define what transactions are valid across the entire network. For
OP_RETURN: - Consensus Rules: AllowOP_RETURNoutputs with data up to the maximum script size (approximately 10,000 bytes) and multiple outputs per transaction (Bitcoin Stack Exchange). - Standardness Rules: LimitOP_RETURNdata to 80 bytes and one output per transaction to discourage excessive data storage and maintain network efficiency.Node operators can adjust these policies using settings like
-datacarrier(enables/disablesOP_RETURNrelay) and-datacarriersize(sets the maximum data size, defaulting to 83 bytes to account for theOP_RETURNopcode and pushdata byte). These settings allow flexibility but reflect Bitcoin Core’s default stance on limiting data usage.The Proposal: Pull Request #32406
Bitcoin Core pull request #32406, proposed by developer instagibbs, seeks to relax these standardness restrictions (GitHub PR #32406). Key changes include: - Removing Default Size Limits: The default
-datacarriersizewould be uncapped, allowing largerOP_RETURNdata without a predefined limit. - Allowing Multiple Outputs: The restriction to oneOP_RETURNoutput per transaction would be lifted, with the total data size across all outputs subject to a configurable limit. - Deprecating Configuration Options: The-datacarrierand-datacarriersizesettings are marked as deprecated, signaling potential removal in future releases, which could limit node operators’ ability to enforce custom restrictions.This proposal does not alter consensus rules, meaning miners and nodes can already accept transactions with larger or multiple
OP_RETURNoutputs. Instead, it changes Bitcoin Core’s default relay policy to align with existing practices, such as miners accepting non-standard transactions via services like Marathon Digital’s Slipstream (CoinDesk).Node Operator Flexibility
Currently, node operators can customize
OP_RETURNhandling: - Default Settings: Relay transactions with oneOP_RETURNoutput up to 80 bytes. - Custom Settings: Operators can disableOP_RETURNrelay (-datacarrier=0) or adjust the size limit (e.g.,-datacarriersize=100). These options remain in #32406 but are deprecated, suggesting that future Bitcoin Core versions might not support such customization, potentially standardizing the uncapped policy.Arguments in Favor of Relaxing Limits
Supporters of pull request #32406 and similar proposals argue that the current restrictions are outdated and ineffective. Their key points include: - Ineffective Limits: Developers bypass the 80-byte limit using methods like Inscriptions, which store data in other transaction parts, often at higher cost and inefficiency (BitcoinDev Mailing List). Relaxing
OP_RETURNcould channel data into a more efficient format. - Preventing UTXO Bloat: By encouragingOP_RETURNuse, which doesn’t affect the UTXO set, the proposal could reduce reliance on harmful alternatives like unspendable Taproot outputs used by projects like Citrea’s Clementine bridge. - Supporting Innovation: Projects like Citrea require more data (e.g., 144 bytes) for security proofs, and relaxed limits could enable new Layer 2 solutions (CryptoSlate). - Code Simplification: Developers like Peter Todd argue that these limits complicate Bitcoin Core’s codebase unnecessarily (CoinGeek). - Aligning with Practice: Miners already process non-standard transactions, and uncapping defaults could improve fee estimation and reduce reliance on out-of-band services, as noted by ismaelsadeeq in the pull request discussion.In the GitHub discussion, developers like Sjors and TheCharlatan expressed support (Concept ACK), citing these efficiency and innovation benefits.
Arguments Against Relaxing Limits
Opponents, including prominent developers and community members, raise significant concerns about the implications of these changes: - Deviation from Bitcoin’s Purpose: Critics like Luke Dashjr, who called the proposal “utter insanity,” argue that Bitcoin’s base layer should prioritize peer-to-peer cash, not data storage (CoinDesk). Jason Hughes warned it could turn Bitcoin into a “worthless altcoin” (BeInCrypto). - Blockchain Bloat: Additional data increases the storage and processing burden on full nodes, potentially making node operation cost-prohibitive and threatening decentralization (CryptoSlate). - Network Congestion: Unrestricted data could lead to “spam” transactions, raising fees and hindering Bitcoin’s use for financial transactions. - Risk of Illicit Content: The timechain’s immutability means data, including potentially illegal or objectionable content, is permanently stored on every node. The 80-byte limit acts as a practical barrier, and relaxing it could exacerbate this issue. - Preserving Consensus: Developers like John Carvalho view the limits as a hard-won community agreement, not to be changed lightly.
In the pull request discussion, nsvrn and moth-oss expressed concerns about spam and centralization, advocating for gradual changes. Concept NACKs from developers like wizkid057 and Luke Dashjr reflect strong opposition.
Community Feedback
The GitHub discussion for pull request #32406 shows a divided community: - Support (Concept ACK): Sjors, polespinasa, ismaelsadeeq, miketwenty1, TheCharlatan, Psifour. - Opposition (Concept NACK): wizkid057, BitcoinMechanic, Retropex, nsvrn, moth-oss, Luke Dashjr. - Other: Peter Todd provided a stale ACK, indicating partial or outdated support.
Additional discussions on the BitcoinDev mailing list and related pull requests (e.g., #32359 by Peter Todd) highlight similar arguments, with #32359 proposing a more aggressive removal of all
OP_RETURNlimits and configuration options (GitHub PR #32359).| Feedback Type | Developers | Key Points | |---------------|------------|------------| | Concept ACK | Sjors, ismaelsadeeq, others | Improves efficiency, supports innovation, aligns with mining practices. | | Concept NACK | Luke Dashjr, wizkid057, others | Risks bloat, spam, centralization, and deviation from Bitcoin’s purpose. | | Stale ACK | Peter Todd | Acknowledges proposal but with reservations or outdated support. |
Workarounds and Their Implications
The existence of workarounds, such as Inscriptions, which exploit SegWit discounts to embed data, is a key argument for relaxing
OP_RETURNlimits. These methods are costlier and less efficient, often costing more thanOP_RETURNfor data under 143 bytes (BitcoinDev Mailing List). Supporters argue that formalizing largerOP_RETURNdata could streamline these use cases. Critics, however, see workarounds as a reason to strengthen, not weaken, restrictions, emphasizing the need to address underlying incentives rather than accommodating bypasses.Ecosystem Pressures
External factors influence the debate: - Miners: Services like Marathon Digital’s Slipstream process non-standard transactions for a fee, showing that market incentives already bypass standardness rules. - Layer 2 Projects: Citrea’s Clementine bridge, requiring more data for security proofs, exemplifies the demand for relaxed limits to support innovative applications. - Community Dynamics: The debate echoes past controversies, like the Ordinals debate, where data storage via inscriptions raised similar concerns about Bitcoin’s purpose (CoinDesk).
Bitcoin’s Identity at Stake
The
OP_RETURNdebate is not merely technical but philosophical, questioning whether Bitcoin should remain a focused monetary system or evolve into a broader data platform. Supporters see relaxed limits as a pragmatic step toward efficiency and innovation, while opponents view them as a risk to Bitcoin’s decentralization, accessibility, and core mission. The community’s decision will have lasting implications, affecting node operators, miners, developers, and users.Conclusion
As Bitcoin navigates this crossroads, the community must balance the potential benefits of relaxed
OP_RETURNlimits—such as improved efficiency and support for new applications—against the risks of blockchain bloat, network congestion, and deviation from its monetary roots. The ongoing discussion, accessible via pull request #32406 on GitHub (GitHub PR #32406). Readers are encouraged to explore the debate and contribute to ensuring that any changes align with Bitcoin’s long-term goals as a decentralized, secure, and reliable system. -
 @ 57d1a264:69f1fee1
2025-05-07 06:56:25
@ 57d1a264:69f1fee1
2025-05-07 06:56:25Wild parrots tend to fly in flocks, but when kept as single pets, they may become lonely and bored https://www.youtube.com/watch?v=OHcAOlamgDc
Source: https://www.smithsonianmag.com/smart-news/scientists-taught-pet-parrots-to-video-call-each-other-and-the-birds-loved-it-180982041/
originally posted at https://stacker.news/items/973639
-
 @ 57d1a264:69f1fee1
2025-05-07 06:29:52
@ 57d1a264:69f1fee1
2025-05-07 06:29:52Your device, your data. TRMNL's architecture prevents outsiders (including us) from accessing your local network. TRMNAL achieve this through 1 way communication between client and server, versus the other way around. Learn more.
Learn more at https://usetrmnl.com/
originally posted at https://stacker.news/items/973632
-
 @ 57d1a264:69f1fee1
2025-05-07 06:16:30
@ 57d1a264:69f1fee1
2025-05-07 06:16:30Here’s Sean Voisen writing about how programming is a feeling:
For those of us who enjoy programming, there is a deep satisfaction that comes from solving problems through well-written code, a kind of ineffable joy found in the elegant expression of a system through our favorite syntax. It is akin to the same satisfaction a craftsperson might find at the end of the day after toiling away on well-made piece of furniture, the culmination of small dopamine hits that come from sweating the details on something and getting them just right. Maybe nobody will notice those details, but it doesn’t matter. We care, we notice, we get joy from the aesthetics of the craft.
This got me thinking about the idea of satisfaction in craft. Where does it come from?
Continue Reading https://blog.jim-nielsen.com/2025/craft-and-satisfaction/
originally posted at https://stacker.news/items/973628
-
 @ 57d1a264:69f1fee1
2025-05-07 06:03:29
@ 57d1a264:69f1fee1
2025-05-07 06:03:29CryptPad
Collaboration and privacy. Yes, you can have both Flagship instance of CryptPad, the end-to-end encrypted and open-source collaboration suite. Cloud administered by the CryptPad development team. https://cryptpad.fr/
ONLYOFFICE DocSpace
Document collaboration made simpler. Easily collaborate with customizable rooms. Edit any content you have. Work faster using AI assistants. Protect your sensitive business data. Download or try STARTUP Cloud (Limited-time offer) FREE https://www.onlyoffice.com/
SeaFile
A new way to organize your files Beyond just syncing and sharing files, Seafile lets you add custom file properties and organize your files in different views. With AI-powered automation for generating properties, Seafile offers a smarter, more efficient way to manage your files. Try it Now, Free for up to 3 users https://seafile.com/
SandStorm
An open source platform for self-hosting web apps Self-host web-based productivity apps easily and securely. Sandstorm is an open source project built by a community of volunteers with the goal of making it really easy to run open source web applications. Try the Demo or Signup Free https://alpha.sandstorm.io/apps
NextCloud Hub
A new generation of online collaboration that puts you in control. Nextcloud offers a modern, on premise content collaboration platform with real-time document editing, video chat & groupware on mobile, desktop and web. Sign up for a free Nextcloud account https://nextcloud.com/sign-up/
LinShare
True Open Source Secure File Sharing Solution We are committed to providing a reliable Open Source file-sharing solution, expertly designed to meet the highest standards of diverse industries, such as government and finance Try the Demo https://linshare.app/
Twake Drive
The open-source alternative to Google Drive. Privacy-First Open Source Workplace. Twake workplace open source business. Improve your effeciency with truly Open Source, all-in-one digital suite. Enhance the security in every aspect of your professional and private life. Sign up https://sign-up.twake.app/
SpaceDrive
One Explorer. All Your Files. Unify files from all your devices and clouds into a single, easy-to-use explorer. Designed for creators, hoarders and the painfully disorganized. Download desktop app (mobile coming soon) https://www.spacedrive.com/
ente
Safe Home for your photos Store, share, and discover your memories with end-to-end encryption. End-to-end encryption, durable storage and simple sharing. Packed with these and much more into our beautiful open source apps. Get started https://web.ente.io
fileStash
Turn your FTP server into... Filestash is the enterprise-grade file manager connecting your storage with your identity provider and authorisations. Try the demo https://demo.filestash.app
STORJ
Disruptively fast. Globally secure. S3-compatible distributed cloud services that make the most demanding workflows fast and affordable. Fast track your journey toward high performance cloud services. Storj pricing is consistent and competitive in meeting or exceeding your cloud services needs. Give the products a try to experience the benefits of the distributed cloud. Get Started https://www.storj.io/get-started
FireFile
The open‑source alternative to Dropbox. Firefiles lets you setup a cloud drive with the backend of your choice and lets you seamlessly manage your files across multiple providers. It revolutionizes cloud storage management by offering a unified platform for all your storage needs. Sign up Free https://beta.firefiles.app
originally posted at https://stacker.news/items/973626
-
 @ 57d1a264:69f1fee1
2025-05-06 06:00:25
@ 57d1a264:69f1fee1
2025-05-06 06:00:25Album art didn’t always exist. In the early 1900s, recorded music was still a novelty, overshadowed by sales of sheet music. Early vinyl records were vastly different from what we think of today: discs were sold individually and could only hold up to four minutes of music per side. Sometimes, only one side of the record was used. One of the most popular records of 1910, for example, was “Come, Josephine, in My Flying Machine”: it clocked in at two minutes and 39 seconds.
The invention of album art can get lost in the story of technological mastery. But among all the factors that contributed to the rise of recorded music, it stands as one of the few that was wholly driven by creators themselves. Album art — first as marketing material, then as pure creative expression — turned an audio-only medium into a multi-sensory experience.
This is the story of the people who made music visible.
originally posted at https://stacker.news/items/972642
-
 @ bbef5093:71228592
2025-05-07 15:09:39
@ bbef5093:71228592
2025-05-07 15:09:39Az Európai Bizottság terve az orosz urán- és energiafüggőség felszámolására
Az Európai Bizottság bejelentette, hogy korlátozni kívánja az új urán-, dúsított urán- és egyéb, Oroszországból származó nukleáris anyagokra vonatkozó ellátási szerződéseket, ezzel is elősegítve, hogy az Európai Unió „teljesen megszüntesse” az orosz energiától való függését[8][6][2].
A Bizottság új ütemtervet mutatott be, amely részletesen tartalmazza, hogyan kívánja megszüntetni az orosz energiafüggőséget, miközben biztosítja az EU energiaellátásának és árainak stabilitását[6][2][15].
Főbb intézkedések és célok
- Az EU az orosz gázimport arányát 45%-ról 19%-ra csökkentette a 2022 májusában indított REPowerEU tervnek köszönhetően, de 2024-ben ismét növekedett az orosz gáz behozatala[2][20].
- Az új ütemterv szerint az orosz olaj, gáz és nukleáris energia fokozatosan, összehangoltan és biztonságosan kerül ki az uniós piacokról, miközben az EU a tiszta energiára való átállást gyorsítja fel[6][15][7].
- Az EU-tagállamoknak 2025 végéig nemzeti terveket kell készíteniük arról, hogyan járulnak hozzá az orosz gáz, nukleáris energia és olaj importjának megszüntetéséhez[13][7][18].
- Az orosz eredetű urán, dúsított urán és egyéb nukleáris anyagok esetében új korlátozásokat vezetnek be: az Euratom Ellátási Ügynökség (ESA) nem hagy jóvá új orosz beszállítási szerződéseket, és gazdasági eszközökkel is igyekeznek visszaszorítani az importot[4][5][16].
- A meglévő rövid távú szerződéseket 2025 végéig meg kell szüntetni, új szerződéseket pedig nem lehet kötni; a hosszú távú szerződéseket 2027 végéig kell felmondani[5][7][6].
- Az intézkedések célja, hogy a teljes orosz gáz- és olajimport 2027 végéig megszűnjön, az orosz atomenergia pedig fokozatosan kivezetésre kerüljön[3][9][17].
Nukleáris háttér
- Az ESA jelentése szerint 2023-ban az EU-ban felhasznált természetes urán 23,4%-a érkezett Oroszországból, ami 72,6%-os növekedést jelentett, főként a VVER típusú orosz atomerőművek üzemanyag-felhalmozása miatt[16].
- Az EU-ban 19 VVER reaktor működik (Bulgáriában, Csehországban, Finnországban, Magyarországon és Szlovákiában).
- Az EU természetes uránszükséglete a globális igények mintegy 22%-át teszi ki, a beszerzések 91%-a Kanadából, Oroszországból, Kazahsztánból és Nigerből származik[16].
Célkitűzés és indoklás
A Bizottság szerint az orosz energiafüggőség felszámolása nemcsak gazdasági, hanem biztonságpolitikai kérdés is, mivel Oroszország többször is eszközként használta az energiát az EU-val szemben[2][12]. A lépések célja, hogy az EU energiaellátása biztonságos, stabil és kiszámítható maradjon, miközben az orosz energiaimportból származó bevételek ne finanszírozhassák tovább az Ukrajna elleni háborút[6][2][12].
Források alapján készült magyar összefoglaló és fordítás
Citations: [1] Döntött az Európai Bizottság: teljes mértékben megszüntetik ... - 444 https://444.hu/2025/05/06/dontott-az-europai-bizottsag-teljes-mertekben-megszuntetik-az-orosz-energiatol-valo-fuggest [2] Három éven belül felszámolná az orosz energiafüggőséget az ... https://hu.euronews.com/my-europe/2025/05/06/harom-even-belul-felszamolna-az-orosz-energiafuggoseget-az-europai-bizottsag [3] 2027-re teljesen leállítaná az Európai Bizottság az orosz ... - Új Szó https://ujszo.com/kozelet/2027-re-teljesen-leallitana-az-europai-bizottsag-az-orosz-energiabehozatalt-a-nuklearis [4] Bejelentették Brüsszelben: megkerülik Magyarországot, teljesen ... https://www.portfolio.hu/gazdasag/20250506/bejelentettek-brusszelben-megkerulik-magyarorszagot-teljesen-levalik-az-orosz-olajrol-es-gazrol-az-eu-759267 [5] Érik az újabb ütközés: Brüsszel betiltaná az orosz energiát https://www.valaszonline.hu/2025/05/06/energia-szankcio-oroszorszag-haboru-eu-olaj-gaz-uran/ [6] Az EU teljes mértékben megszünteti az orosz energiától való függését https://hungary.representation.ec.europa.eu/az-eu-teljes-mertekben-megszunteti-az-orosz-energiatol-valo-fuggeset-2025-05-06_hu?prefLang=en [7] Megvan az ütemterv, végleg betiltaná az orosz energiát az Európai ... https://index.hu/kulfold/2025/05/06/orosz-energiafuggoseg-orosz-gaz-olaj-import-europai-unio-repowereu/ [8] European Commission Unveils Plans To Restrict New Uranium ... https://www.nucnet.org/news/european-commission-unveils-plans-to-restrict-new-uranium-deals-with-russia-5-3-2025 [9] Az EU teljes mértékben megszünteti az orosz energiától való ... https://infostart.hu/belfold/2025/05/06/az-eu-teljes-mertekben-megszunteti-az-orosz-energiatol-valo-fuggoseget-a-nap-hirei [10] [PDF] EURÓPAI BIZOTTSÁG Brüsszel, 2025.4.9. COM(2025) 159 final ... https://secure.ipex.eu/IPEXL-WEB/download/file/082d29089612ec1e019619f955940250 [11] Kiszivárgott az Európai Bizottság 2025-ös munkaprogramja https://www.eu-monitor.hu/hu/cikk/20250206-kiszivargott-az-europai-bizottsag-2025-os-munkaprogramja [12] EU says it will end dependency on Russian energy supplies https://www3.nhk.or.jp/nhkworld/en/news/20250507_B4/ [13] Végleg leválik az orosz energiáról az Európai Unió ... - Népszava https://nepszava.hu/3278673_oroszorszag-europai-unio-foldgaz-koolaj-levalas-terv [14] Egyre több európai ország támogatja az atomenergiát https://www.vg.hu/nemzetkozi-gazdasag/2025/03/atomenergia-energiatarolas-europa [15] Az EU teljes mértékben megszünteti az orosz energiától való ... https://karpatinfo.net/energiafuggetlenseg-orosz-foldgaz-orosz-energiafuggoseg-2025-05-07 [16] EU outlines measures to end Russian gas, oil imports by end-2027 https://balkangreenenergynews.com/eu-outlines-measures-to-end-russian-gas-oil-imports-by-end-2027/ [17] Az Európai Unió 2027 végére betiltaná az orosz gáz importját https://www.korkep.sk/cikkek/gazdasag/2025/05/05/az-europai-unio-2027-vegere-betiltana-az-orosz-gazimportot/ [18] Ficónak és Orbánnak sem tetszik, hogy az EU teljesen kitiltaná az ... https://napunk.dennikn.sk/hu/4623240/ficonak-es-orbannak-sem-tetszik-hogy-az-eu-teljesen-kitiltana-az-orosz-energiat/ [19] Várhelyi Olivér késlelteti az EU orosz energiafüggőségét felszámoló ... https://telex.hu/kulfold/2025/05/05/varhelyi-oliver-europai-bizottsag-orosz-energia-kivaltas-hatraltatas [20] REPowerEU roadmap - Energy - European Commission https://energy.ec.europa.eu/strategy/repowereu-roadmap_en
-
 @ 9c9d2765:16f8c2c2
2025-05-07 12:39:48
@ 9c9d2765:16f8c2c2
2025-05-07 12:39:48CHAPTER FIFTEEN
"Have you seen the news?" Sandra’s voice crackled through the phone, her tone urgent and unsettled.
James, seated in his office at JP Enterprises, furrowed his brows. He hadn’t turned on the television yet. "No. What happened?"
"You need to check the headlines immediately. It’s everywhere. They’ve dragged your name through the mud!"
Without another word, James reached for the remote and turned on the large flat-screen mounted on his office wall. The screen lit up with a news report, the broadcaster’s voice sharp and sensational.
“Shocking footage surfaces: JP Enterprises’ President humiliates his only sister in broad daylight!”
Photos of James and Evelyn outside the company played in a dramatic sequence him confronting her, her being escorted out, and his seemingly cold expression. The captions twisted the story:
“Heartless Billionaire?” “President throws out helpless sister for asking money” “The shameful side of JP Enterprises’ leader exposed!”
James leaned back in his chair, eyes narrowing as he watched.
"This is calculated," he muttered under his breath. "Scripted. Twisted."
He turned off the screen and called Sandra back. "I want Tracy's devices checked. Every message, every image. And I want a full trace on the origin of this story. Media outlets don’t run this kind of narrative without a source."
"You think Tracy’s behind it?" Sandra asked, her voice low.
"She took the pictures, I’m sure of it. But she’s not working alone," James replied, voice steely. "This is too well-planned for one person. They’re trying to frame me, twist reality, and attack my image. And I’ll make sure every single one of them is exposed."
Meanwhile, at a discreet location, Mark, Helen, and Tracy gathered to watch the fire they had ignited. Tracy grinned as she scrolled through social media posts and reactions.
"It’s gone viral," she said gleefully. "Everyone thinks that woman’s your sister. It’s everywhere on blogs, gossip pages, even official news networks. The damage is done."
Mark chuckled darkly. "This will shatter his reputation. Let’s see how he enjoys being publicly hated."
Helen, sipping her wine with a satisfied look, added, "It’s only the beginning. Let’s push this narrative harder. We’ll make sure the board at JP Enterprises starts questioning his character."
But little did they know James had already activated his private investigative team. Every file, every message, every trail was being traced.
Back at JP Enterprises, James stood by the window of his office, watching the skyline, his hands in his pockets.
"They want a war?" he said to himself quietly. "Then I’ll give them one. But on my own terms."
His phone buzzed. A message from his chief of cyber-security read:
“We’ve located the media contact. Payment traced to a dummy account linked to Helen Ray.”
James stared at the screen, his jaw tightening.
The day of the much-anticipated 16th Anniversary of JP Enterprises finally arrived, cloaked in glamour, prestige, and tension. The event venue, a grand luxury hall draped in velvet and golden decor, radiated elegance and opulence. Bright lights illuminated the red carpet, and camera flashes sparked like lightning as influential business magnates, city officials, and esteemed guests from far and wide began to pour in.
Among the prominent guests were Helen Ray, Mark, Tracy, and other members of the Ray family. Dressed in designer gowns and tailored suits, they mingled with high society, laughing and sipping champagne, their polished facades hiding the scheme they had carefully orchestrated for the night.
The hall buzzed with anticipation for the arrival of Mr. and Mrs. JP, the founders of the JP Empire. Meanwhile, in a secluded corner of the hall, Helen leaned towards Mark, whispering with a smirk, “She’s on her way. Get ready for the show.”
The “she” Helen referred to was Evelyn, the same woman they had bribed to once again impersonate James’s sister and stir public humiliation. This time, it wouldn’t just be a few photos, they wanted a scandal of epic proportions, a scene so chaotic and public that it would crumble James’s standing in the business world for good.
As guests chatted and live music flowed through the air, James entered the hall in a pristine black tuxedo, exuding power and poise. He walked beside his uncle Charles and his loyal staff, warmly greeting dignitaries and longtime associates. His presence commanded attention, but murmurs soon rippled through the crowd.
Whispers filled the air like wind in dry grass:
"That’s the man from the headline, isn’t he?" "They say he threw his own sister out for asking for help." "Such cruelty… and yet here he is, smiling like a saint."
As James navigated through the crowd with measured grace, Helen sauntered over, her heels clicking on the marble floor, her expression dripping with sarcasm.
“Well, well, if it isn’t our gallant President,” she began, feigning admiration. “I must say, you clean up well for someone who was just exposed in the most shameful news of the year.”
James turned to her with a calm but unreadable gaze. “Helen,” he greeted curtly.
She chuckled. “You really should be more careful with family matters. The public has a long memory, you know.”
Before James could reply, a loud voice broke through the soft music. “James! James! You left me with nothing!”
All heads turned toward the entrance, where Evelyn stumbled in, her appearance carefully staged to look disheveled and distraught. She weaved through the crowd, screaming and sobbing uncontrollably, clutching at the air as security hesitated to intervene.
“Please! I’m your sister! I just needed a little help!” she cried dramatically. “How could you do this to your own blood?!”
Gasps echoed through the grand hall.
Guests froze in place, their judgmental stares directed at James. Cameraman didn’t hesitate to raise their lenses. Phones were pulled out. A social media storm was already brewing in real time.
James stood still, eyes narrowed. He didn’t move, didn’t speak.
Tracy, standing beside Helen, discreetly snapped more photos, already typing up the next round of false headlines to feed into the media engine.
Helen smirked at the chaos and whispered, “This is it. The downfall begins.”
But James wasn’t shaken.
With quiet authority, he raised his hand, and two personal bodyguards appeared from the sidelines. He looked Evelyn square in the eye, then said, loud enough for the nearest guests to hear, “Escort this woman outside. She is not my sister. And she has no place here.”
Evelyn’s cries turned more dramatic, but it was clear to the more discerning eyes in the room that something about her act was off. Her appearance was too deliberate, her performance too exaggerated.
As security led her away, some guests began to murmur with skepticism.
“Wait… that woman doesn’t even resemble him.” “Isn’t it strange she showed up right after that story went viral?” “Could this be a setup?”
-
 @ d61f3bc5:0da6ef4a
2025-05-06 01:37:28
@ d61f3bc5:0da6ef4a
2025-05-06 01:37:28I remember the first gathering of Nostr devs two years ago in Costa Rica. We were all psyched because Nostr appeared to solve the problem of self-sovereign online identity and decentralized publishing. The protocol seemed well-suited for textual content, but it wasn't really designed to handle binary files, like images or video.
The Problem
When I publish a note that contains an image link, the note itself is resilient thanks to Nostr, but if the hosting service disappears or takes my image down, my note will be broken forever. We need a way to publish binary data without relying on a single hosting provider.
We were discussing how there really was no reliable solution to this problem even outside of Nostr. Peer-to-peer attempts like IPFS simply didn't work; they were hopelessly slow and unreliable in practice. Torrents worked for popular files like movies, but couldn't be relied on for general file hosting.
Awesome Blossom
A year later, I attended the Sovereign Engineering demo day in Madeira, organized by Pablo and Gigi. Many projects were presented over a three hour demo session that day, but one really stood out for me.
Introduced by hzrd149 and Stu Bowman, Blossom blew my mind because it showed how we can solve complex problems easily by simply relying on the fact that Nostr exists. Having an open user directory, with the corresponding social graph and web of trust is an incredible building block.
Since we can easily look up any user on Nostr and read their profile metadata, we can just get them to simply tell us where their files are stored. This, combined with hash-based addressing (borrowed from IPFS), is all we need to solve our problem.
How Blossom Works
The Blossom protocol (Blobs Stored Simply on Mediaservers) is formally defined in a series of BUDs (Blossom Upgrade Documents). Yes, Blossom is the most well-branded protocol in the history of protocols. Feel free to refer to the spec for details, but I will provide a high level explanation here.
The main idea behind Blossom can be summarized in three points:
- Users specify which media server(s) they use via their public Blossom settings published on Nostr;
- All files are uniquely addressable via hashes;
- If an app fails to load a file from the original URL, it simply goes to get it from the server(s) specified in the user's Blossom settings.
Just like Nostr itself, the Blossom protocol is dead-simple and it works!
Let's use this image as an example:
 If you look at the URL for this image, you will notice that it looks like this:
If you look at the URL for this image, you will notice that it looks like this:blossom.primal.net/c1aa63f983a44185d039092912bfb7f33adcf63ed3cae371ebe6905da5f688d0.jpgAll Blossom URLs follow this format:
[server]/[file-hash].[extension]The file hash is important because it uniquely identifies the file in question. Apps can use it to verify that the file they received is exactly the file they requested. It also gives us the ability to reliably get the same file from a different server.
Nostr users declare which media server(s) they use by publishing their Blossom settings. If I store my files on Server A, and they get removed, I can simply upload them to Server B, update my public Blossom settings, and all Blossom-capable apps will be able to find them at the new location. All my existing notes will continue to display media content without any issues.
Blossom Mirroring
Let's face it, re-uploading files to another server after they got removed from the original server is not the best user experience. Most people wouldn't have the backups of all the files, and/or the desire to do this work.
This is where Blossom's mirroring feature comes handy. In addition to the primary media server, a Blossom user can set one one or more mirror servers. Under this setup, every time a file is uploaded to the primary server the Nostr app issues a mirror request to the primary server, directing it to copy the file to all the specified mirrors. This way there is always a copy of all content on multiple servers and in case the primary becomes unavailable, Blossom-capable apps will automatically start loading from the mirror.
Mirrors are really easy to setup (you can do it in two clicks in Primal) and this arrangement ensures robust media handling without any central points of failure. Note that you can use professional media hosting services side by side with self-hosted backup servers that anyone can run at home.
Using Blossom Within Primal
Blossom is natively integrated into the entire Primal stack and enabled by default. If you are using Primal 2.2 or later, you don't need to do anything to enable Blossom, all your media uploads are blossoming already.
To enhance user privacy, all Primal apps use the "/media" endpoint per BUD-05, which strips all metadata from uploaded files before they are saved and optionally mirrored to other Blossom servers, per user settings. You can use any Blossom server as your primary media server in Primal, as well as setup any number of mirrors:
 ## Conclusion
## ConclusionFor such a simple protocol, Blossom gives us three major benefits:
- Verifiable authenticity. All Nostr notes are always signed by the note author. With Blossom, the signed note includes a unique hash for each referenced media file, making it impossible to falsify.
- File hosting redundancy. Having multiple live copies of referenced media files (via Blossom mirroring) greatly increases the resiliency of media content published on Nostr.
- Censorship resistance. Blossom enables us to seamlessly switch media hosting providers in case of censorship.
Thanks for reading; and enjoy! 🌸
-
 @ 29156f5e:3627e9c6
2025-05-07 10:16:02
@ 29156f5e:3627e9c6
2025-05-07 10:16:02Trong thế giới giải trí số ngày càng phát triển, ABC88 nổi bật như một nền tảng đáng tin cậy, mang đến trải nghiệm giải trí trực tuyến hoàn hảo cho người dùng. Được xây dựng với công nghệ tiên tiến, ABC88 không chỉ cung cấp giao diện thân thiện, dễ sử dụng mà còn tối ưu hóa hiệu suất để người dùng có thể tận hưởng những giây phút thư giãn mượt mà và không gián đoạn. Nền tảng này phù hợp với tất cả đối tượng người dùng, từ người mới làm quen đến người có kinh nghiệm, nhờ vào sự dễ dàng trong việc điều hướng và truy cập các tính năng. Giao diện của ABC88 không chỉ trực quan mà còn được thiết kế sao cho phù hợp với mọi thiết bị, giúp người dùng dễ dàng tham gia và tương tác dù là qua máy tính hay điện thoại di động. Không chỉ vậy, nền tảng này còn tối ưu hóa tốc độ tải trang và độ mượt mà của các trò chơi, giúp người dùng có thể tận hưởng trải nghiệm giải trí với chất lượng cao mà không phải lo lắng về sự cố kỹ thuật.
ABC88 cung cấp một hệ sinh thái giải trí đa dạng và phong phú, từ các trò chơi sáng tạo, các chương trình giải trí tương tác đến các sự kiện và khuyến mãi đặc biệt. Nền tảng này không chỉ dừng lại ở việc cung cấp những trò chơi cơ bản, mà còn luôn cập nhật những nội dung mới nhất, đáp ứng đầy đủ sở thích của người dùng. Những trò chơi không chỉ mang tính giải trí mà còn giúp người chơi thử thách bản thân, kích thích tư duy sáng tạo và phát triển các kỹ năng cá nhân. Điều này khiến ABC88 trở thành một lựa chọn hấp dẫn không chỉ cho những ai muốn tìm một không gian thư giãn, mà còn cho những người muốn học hỏi và trải nghiệm những thử thách mới. Bên cạnh đó, các chương trình khuyến mãi và sự kiện đặc biệt của ABC88 được tổ chức thường xuyên, mang đến cho người dùng cơ hội nhận những phần quà giá trị. Những sự kiện này không chỉ là cơ hội để người tham gia có thể giành được các giải thưởng hấp dẫn mà còn là cơ hội để họ kết nối với cộng đồng người chơi, tạo ra một môi trường giải trí sôi động và đầy thú vị.
Không chỉ chú trọng vào nội dung và tính năng, ABC88 còn đặc biệt quan tâm đến vấn đề bảo mật và an toàn của người dùng. Với việc sử dụng các công nghệ bảo mật hiện đại, nền tảng này cam kết bảo vệ mọi thông tin cá nhân của người dùng một cách tối đa, giúp người tham gia yên tâm tuyệt đối khi tham gia các hoạt động trên nền tảng. Các giao dịch tài chính và thông tin cá nhân đều được mã hóa và bảo vệ an toàn, tránh xa những nguy cơ tiềm ẩn từ các cuộc tấn công mạng. Bên cạnh đó, đội ngũ hỗ trợ khách hàng của ABC88 luôn sẵn sàng hỗ trợ người dùng 24/7, giúp giải đáp mọi thắc mắc và xử lý nhanh chóng mọi vấn đề phát sinh trong quá trình sử dụng. Chất lượng dịch vụ khách hàng là một yếu tố quan trọng giúp ABC88 ghi điểm với người dùng, bởi người tham gia không chỉ cần một nền tảng giải trí tốt mà còn mong muốn nhận được sự hỗ trợ nhiệt tình và kịp thời. Chính vì vậy, ABC88 luôn không ngừng cải tiến và nâng cao chất lượng dịch vụ của mình để mang đến cho người dùng trải nghiệm tốt nhất.
-
 @ 57d1a264:69f1fee1
2025-05-06 05:49:01
@ 57d1a264:69f1fee1
2025-05-06 05:49:01I don’t like garlic. It’s not a dislike for the taste in the moment, so much as an extreme dislike for the way it stays with you—sometimes for days—after a particularly garlicky meal.
Interestingly enough, both of my brothers love garlic. They roast it by itself and keep it at the ready so they can have a very strong garlic profile in their cooking. When I prepare a dish, I don’t even see garlic on the ingredient list. I’ve cut it out of my life so completely that my brain genuinely skips over it in recipes. While my brothers are looking for ways to sneak garlic into everything they make, I’m subconsciously avoiding it altogether.
A few years back, when I was digging intensely into how design systems mature, I stumbled on the concept of a design system origin story. There are two extreme origin stories and an infinite number of possibilities between. On one hand you have the grassroots system, where individuals working on digital products are simply trying to solve their own daily problems. They’re frustrated with having to go cut and paste elements from past designs or with recreating the same layouts over and over, so they start to work more systematically. On the other hand, you have the top down system, where leadership is directing teams to take a more systematic approach, often forming a small partially dedicated core team to tackle some centralized assets and guidelines for all to follow. The influences in those early days bias a design system in interesting and impactful ways.
We’ve established that there are a few types of bias that are either intentionally or unintentionally embedded into our design systems. Acknowledging this is a great first step. But, what’s the impact of this? Does it matter?
I believe there are a few impacts design system biases, but there’s one that stands out. The bias in your design system makes some individuals feel the system is meant for them and others feel it’s not. This is a problem because, a design system cannot live up to it’s expected value until it is broadly in use. If individuals feel your design system is not for them, the won’t use it. And, as you know, it doesn’t matter how good your design system is if nobody is using it.
originally posted at https://stacker.news/items/972641
-
 @ 57d1a264:69f1fee1
2025-05-05 05:26:34
@ 57d1a264:69f1fee1
2025-05-05 05:26:34The European Accessibility Act is coming, now is a great time for accessibility trainings!. In my Accessibility for Designer workshop, you will learn how to design accessible mockups that prevent issues in visual design, interactions, navigation, and content. You will be able to spot problems early, fix them in your designs, and communicate accessibility clearly with your team. This is a practical workshop with hands-on exercises, not just theory. You’ll actively apply accessibility principles to real design scenarios and mockups. And will get access to my accessibility resources: checklists, annotation kits and more.
When? 4 sessions of 2 hours + Q and As, on: - Mon, June 16, - Tue, June 17, Mon, - June 23 and Tue, - June 24. 9:30 – 12:00 PM PT or 18:30 – 21:00 CET
Register with 15% discount ($255) https://ti.to/smashingmagazine/online-workshops-2022/with/87vynaoqc0/discount/welcometomyworkshop
originally posted at https://stacker.news/items/971772
-
 @ 57d1a264:69f1fee1
2025-05-05 05:15:02
@ 57d1a264:69f1fee1
2025-05-05 05:15:02Crabtree's Framework for Evaluating Human-Centered Research
Picture this: You've spent three weeks conducting qualitative research for a finance app redesign. You carefully recruited 12 participants, conducted in-depth interviews, and identified patterns around financial anxiety and decision paralysis. You're excited to present your findings when the inevitable happens:
"But are these results statistically significant?"
"Just 12 people? How can we make decisions that affect thousands of users based on conversations with just 12 people?"
As UX professionals, we regularly face stakeholders who evaluate our qualitative research using criteria designed for quantitative methods... This misalignment undermines the unique value qualitative research brings to product development.
Continue reading https://uxpsychology.substack.com/p/beyond-numbers-how-to-properly-evaluate
originally posted at https://stacker.news/items/971767
-
 @ 2183e947:f497b975
2025-05-01 22:33:48
@ 2183e947:f497b975
2025-05-01 22:33:48Most darknet markets (DNMs) are designed poorly in the following ways:
1. Hosting
Most DNMs use a model whereby merchants fill out a form to create their listings, and the data they submit then gets hosted on the DNM's servers. In scenarios where a "legal" website would be forced to censor that content (e.g. a DMCA takedown order), DNMs, of course, do not obey. This can lead to authorities trying to find the DNM's servers to take enforcement actions against them. This design creates a single point of failure.
A better design is to outsource hosting to third parties. Let merchants host their listings on nostr relays, not on the DNM's server. The DNM should only be designed as an open source interface for exploring listings hosted elsewhere, that way takedown orders end up with the people who actually host the listings, i.e. with nostr relays, and not with the DNM itself. And if a nostr relay DOES go down due to enforcement action, it does not significantly affect the DNM -- they'll just stop querying for listings from that relay in their next software update, because that relay doesn't work anymore, and only query for listings from relays that still work.
2. Moderation
Most DNMs have employees who curate the listings on the DNM. For example, they approve/deny listings depending on whether they fit the content policies of the website. Some DNMs are only for drugs, others are only for firearms. The problem is, to approve a criminal listing is, in the eyes of law enforcement, an act of conspiracy. Consequently, they don't just go after the merchant who made the listing but the moderators who approved it, and since the moderators typically act under the direction of the DNM, this means the police go after the DNM itself.
A better design is to outsource moderation to third parties. Let anyone call themselves a moderator and create lists of approved goods and services. Merchants can pay the most popular third party moderators to add their products to their lists. The DNM itself just lets its users pick which moderators to use, such that the user's choice -- and not a choice by the DNM -- determines what goods and services the user sees in the interface.
That way, the police go after the moderators and merchants rather than the DNM itself, which is basically just a web browser: it doesn't host anything or approve of any content, it just shows what its users tell it to show. And if a popular moderator gets arrested, his list will still work for a while, but will gradually get more and more outdated, leading someone else to eventually become the new most popular moderator, and a natural transition can occur.
3. Escrow
Most DNMs offer an escrow solution whereby users do not pay merchants directly. Rather, during the Checkout process, they put their money in escrow, and request the DNM to release it to the merchant when the product arrives, otherwise they initiate a dispute. Most DNMs consider escrow necessary because DNM users and merchants do not trust one another; users don't want to pay for a product first and then discover that the merchant never ships it, and merchants don't want to ship a product first and then discover that the user never pays for it.
The problem is, running an escrow solution for criminals is almost certain to get you accused of conspiracy, money laundering, and unlicensed money transmission, so the police are likely to shut down any DNM that does this. A better design is to oursource escrow to third parties. Let anyone call themselves an escrow, and let moderators approve escrows just like they approve listings. A merchant or user who doesn't trust the escrows chosen by a given moderator can just pick a different moderator. That way, the police go after the third party escrows rather than the DNM itself, which never touches user funds.
4. Consequences
Designing a DNM along these principles has an interesting consequence: the DNM is no longer anything but an interface, a glorified web browser. It doesn't host any content, approve any listings, or touch any money. It doesn't even really need a server -- it can just be an HTML file that users open up on their computer or smart phone. For two reasons, such a program is hard to take down:
First, it is hard for the police to justify going after the DNM, since there are no charges to bring. Its maintainers aren't doing anything illegal, no more than Firefox does anything illegal by maintaining a web browser that some people use to browse illegal content. What the user displays in the app is up to them, not to the code maintainers. Second, if the police decided to go after the DNM anyway, they still couldn't take it down because it's just an HTML file -- the maintainers do not even need to run a server to host the file, because users can share it with one another, eliminating all single points of failure.
Another consequence of this design is this: most of the listings will probably be legal, because there is more demand for legal goods and services than illegal ones. Users who want to find illegal goods would pick moderators who only approve those listings, but everyone else would use "legal" moderators, and the app would not, at first glance, look much like a DNM, just a marketplace for legal goods and services. To find the illegal stuff that lurks among the abundant legal stuff, you'd probably have to filter for it via your selection of moderators, making it seem like the "default" mode is legal.
5. Conclusion
I think this DNM model is far better than the designs that prevail today. It is easier to maintain, harder to take down, and pushes the "hard parts" to the edges, so that the DNM is not significantly affected even if a major merchant, moderator, or escrow gets arrested. I hope it comes to fruition.
-
 @ 005bc4de:ef11e1a2
2025-05-07 14:19:15
@ 005bc4de:ef11e1a2
2025-05-07 14:19:15The beautiful evil of horse racing

Horse racing intrigues me. And, it appalls me. I find it to be both gloriously beautiful and brutally cruel.
One of the fun facts shared tirelessly around social media for Kentucky Derby #151 was something like this: "This is the first Derby where every horse is in the bloodline of Secretariat." Secretariat, if you don't know, won the Triple Crown in 1973 (KY Derby, Preakness, Belmont) and still holds the fastest times in all three of those races.
That's really a nice fun fact when you first hear it, but maybe it shouldn't be too surprising. After a successful racing career, a male racehorse "retires" to a life of studding himself out, which is where the real horse money is. His post-racing stats: he bred 60 mares per year, he sired 660 foals, and he earned an estimated $120 million in stud fees. When you start branching out the Secretariat family tree over several generations, well, the sheer numbers must be very large. That means the chances that any given Thoroughbred might have a hint of Secretariat blood must get rather high. Grok AI estimates there are 500,000 Thoroughbreds today worldwide, and that beteen 250,000 to 400,000 are in Secretariat's lineage, that's 50% to 80% of every Thoroughbred. Suddenly, the social media snippet from Derby #151 is less surprising, less cool.

Secretariat, retired from racing.
The beautiful side of horse racing
Horse racing is beautiful. This is the easy part to write. If you've ever been to a horse track, especially on a big race day, it's a true multi-sensory experience.
- There are smells that we typically don't smell often in this modern world...especially if you hang out near the paddock. Personally, I don't find horse dung particularly stinky, but earthy.
- There are tastes and good smells. Food and drink are a huge part of horse racing. There is a reason that the Derby has its own pie (a chocolate pecan pie) and each major race has its own drink. Feasting and tailgating are huge parts of horse racing.
- There are things to feel, actually to bodily feel. Aside from crowds of people to bump into, if you stand close to the track, you can feel the reverberation of hooves beating the dirt. We hear the term "thundering herd" sometimes in college sports, but, that term is not just words. You can actually feel the thunder of those hooves.
- The sounds are distinctly horse racing. The announcer's calls of "Less than a minute," "They're in the gates," and "And they're off!" are iconic, not to mention the terms "down to the wire," "won by a nose," or "photo finish." And then there's the bugle's announcement, the singing of "My Old Kentucky Home" at the Derby, the roar of the crowd, and moans of loss from bad bets, shrieks of joy from good bets, and that thunder from the herd, of course.
- The visuals are just stunning. People-wise, the women in their pastel sundresses, the men are snazzy in their colors too (though some go too over-the-top for my liking; they move from classy to clownish), and then there are the hats which are their own category altogether. There's the track, and the spires, and the grass and dirt (or mud) and roses. And there's the jockeys and their colorful silks. But, mostly, there's the horses. A Thoroughbred racehorse at full speed, in full stride, is incredible to look upon. It is a beast that is entirely built for one pure reason: speed. You might be familiar with ESPN's "The Body Issue" that features elite, pro athletes in the nude so that their incredible physiques are displayed. Horse racing is the same thing, equine style. The Derby, in particular, is a sports photographer's bonanza. If you actually know what you're doing, you can't not get great results. Below are some photos amateur me point-and-clicked on Derby Day at a horse track (not Churchill Downs):
!(image)[https://files.peakd.com/file/peakd-hive/crrdlx/Eq7LSG39v5H5NpQppxhzwhfAtJVQikYVppRJsgZXh6KxGXU2YochRXqoJaW7NMZ8Yd8.jpg]
!(image)[https://files.peakd.com/file/peakd-hive/crrdlx/23wWw7ZbXPJxKFAyLwuraK1QypVcLV6QpsyG6Ccr6ZLiPYgNtUBa3ALWx1XR4wPYayhmT.png]
!(image)[https://files.peakd.com/file/peakd-hive/crrdlx/2432HqW3ZtUCjvGD7WTkg2z2ngoByX2rV6htgENN1eytUYXycRCaQdevL7xn1mdKC8qG8.gif]
!(image)[https://files.peakd.com/file/peakd-hive/crrdlx/245HijMM8pQ7c2EdJwrzUPa3LDjm1P51WqU6j5mYkAJnAXJrkbAn6XBNCzR7G28MSR62u.png]
!(image)[https://files.peakd.com/file/peakd-hive/crrdlx/EpVAhnScSoAVCYvw2Faf7ZyipskYLvu9MuBXzmHN3jdVPoDBVAVR8yqrrGf1c7Apxzb.jpg]
!(image)[https://files.peakd.com/file/peakd-hive/crrdlx/245Hm6k5HafqiMfzUiNK7Z3pUG752f4CmLc5pMVuonkQVY1sKG9ucSrdGgvNVQGNud628.gif]
Horse racing appeals to all senses and is viscerally exhilarating in so many ways. It is beautiful.
Genetics
But, let's get back to the real point: this game is all about Brave New World-like breeding and genetics. It is horse eugenics. The idea is simple: fast Mommy horse and fast Daddy horse means fast baby horse. In horse racing, a horse's blood lineage is called its dosage. Personally, I pay zero attention to dosage (I focus on track length and closing the long races), but dosage is a mathematical stat that tries to answer, "How much is this horse truly a Thoroughbred and a genetic winner?" This question of dosage begs another question, "What actually is a Thoroughbred?"
A Thoroughbred is a horse breed. There are a lot of horse breeds, a lot. For a novice like me, it's very hard to distinguish one from another. I think most people can see a difference between a draft horse, bred for pulling heavy loads, and a Thoroughbred, bred for speed. I think most people, if betting on a foot race, would bet on the Thoroughbred below, left and not on "Jupiter, the largest draft horse in America" on the right. If betting on hauling a wagon load of beer up a steep hill, most would bet Jupiter.
!(image)[https://files.peakd.com/file/peakd-hive/crrdlx/23yx8AjtVZkpE7jXJ2RXzV78hhXSvsgU97i2FkvfcFcEZevfshNgwPw2diJNhmL344gmR.png]
But, when comparing racing horses, there are also Sandardbreds which are bred for harness racing and thus have a heavier build than Thoroughbreds. The two breeds are shown below, but their distinctions are not particularly outstanding to my novice eye. Can you tell the difference, which is the Standardbred versus the Thoroughbred? (Answer at the bottom of page.) Maybe side-by-side you can tell, but could you tell if you saw one standing alone? If you saw two of the same breed, could you judge by appearance which one runs faster? If you can, I tip my cap to you.
!(image)[https://files.peakd.com/file/peakd-hive/crrdlx/23zbTqFJgYpKyXwxbGsVeQiKv4tTZSj8S8QboTJWEhTETPqjnaUVDtX2BirjBXH5KVNo6.png]
I imagine most people are much more familiar with, and can more readily notice, the differences in dog breeds. For instance, take the French Bulldog, the Greyhound, or the world's best dog breed, the Labrador Retriever (totally unbiased here).
!(image)[https://files.peakd.com/file/peakd-hive/crrdlx/244oozGkxAwS4sqoWiT8phQv8ssrqq4caB9bHgDufsogds7scUUfhp54WTKmosDzfL5WT.png]
The French Bulldog is bred for cosmetics, the greyhound for pure speed, and the Labrador for all-around everything...intelligence, sturdy athleticism, loyal companionship (totally unbiased here). In these three dogs, we can clearly see the differences that have resulted from breeding.
The evil side of horse racing
Horse racing is evil. And, it is cruel. But, for now, let's step back to the dogs. Dog breeding can be cruel as well.
The French Bulldog is something of the "it" dog right now. A quick Google Gemini search reported it as the most popular breed in 2025.
I remember when "101 Dalmatians" came out 1996. Dalmatians skyrocketed in popularity. But, that popularity was anything but a blessing for Dalmatian pups. They were overbred (and are too inbred as it is), oversold, and were taken in by people eager to get in on the "it" dog then and scoop up the cute spotted pups. But, Dalmatians are very active pups that grow into very active dogs. When the novelty of the spotted pup wore off, many were returned or given away or taken to shelters as being uncontrollable.
The French Poodle situation is not too different. The dogs were bred for little purpose beyond the sin of human vanity. People wanted a short, stocky, smoosh-faced dog that they perceived as cute. And, that's what they got: an unathletic dog that looked a certain way, with middle-of-the-road intelligence, and little use aside from its appearance.
Worse, seeking out this certain "toy dog" look, French Bulldogs suffer from a plethora of health issues. Summed up, they have the lowest life expectancy "by a large margin" of all dogs at only 4.5 years (average is 11.2. years).
There is a neighbor near to me who breeds French Bulldogs. Evidently, it's a lucrative business as they apparently sell for an estimated $2,000 to $8,000 dollars each. I don't know how many litters the neighbor's have bred and pawned, but it has been several. The breeder bitch is constantly given a little trot outside before being hauled to the vet for insemination. (Sadly, this seems to be about the only time she is taken out for exercise and family "fun.") Considering he and his wife have no real job, this seems to be their job. Breed, advertise (complete with foofy tutu outfit photos), market, sell, repeat. With only a 4.5 year life span, I see the lucrative nature in this business.
All told, it's basically a sin and a shame that humans do this to these dogs. A certain segment of people desire a certain unnatural smooshed face in a dog. And because we vainly want a certain look in a dog, so as to accessorize our own look, we breed them into forms unnatural to a canine, curse them with severe breathing difficulties and other serious health issues, and short lives.
A Greyhound is essentially a canine Thoroughbred. From generations of selective breeding, it has a massive chest, long body with a narrow waist, and long, spindly legs. It's sole purpose is speed. Ironically, both the Thoroughbred and Greyhound can race at about the same speed...44 mph, give or take.
Man's sinful nature has abused the Greyhound too. These hounds are racing dogs and racing means gambling. So, dog tracks for have been common. The pups are bred, they race a few years, then they are hopefully adopted out. A good friend of mine once adopted a retired racer to become the family dog. "Bandit" initially had a post-race job as a business's guard dog. But, due to him constantly doing nothing but laying around and sleeping, he was fired as a guard dog (who gets a Greyhound for a guard dog anyway?). Bandit eventually went to my friend, was a bit neurotic, but turned out to be a good family dog.
I think most Greyhounds don't have the fortunate story of Bandit. Once raced out, they're done and forgotten. Man's thrills are fleeting, whatever sparkles in his eye soon fades. To combat the ills of dog racing, I know that the citizens of Florida voted to outlaw dog racing in 2018 (and it indeed ended Dec. 31, 2020). Now, dog tracks lay rusting away, and Greyhounds are largely forgotten.
And then, there's the Labrador Retriever. What's not to like? These dogs can do it all, and they do it all well. Name a dog task, Labs do that well. Full disclosure: I once had a Lab (or rather, half Lab, and half...Great Dane? Doberman? Something?). Her mother was Lab and my dog looked Lab, though a bit taller and leaner. She was incredible. So, yes, I favor Labs.
But, even my beloved Labs and all that they excel in, even Labs have their issues, such as high rates of hip dysplasia. Selective breeding, and a too-narrow gene pool, have consequences.
Back to horses
Let's try to bring this back to horses. Thoroughbreds and horse racing mirror both of the characteristics seen in the French Bulldog and the Greyhound.
- Thoroughbreds have been, and still are, extremely selectively bred to accentuate certain qualities: speed, speed, speed.
- Thoroughbreds are bred for money. Literally, a champion stud or mare doesn't breed for free.
Regarding speed, Thoroughbreds have a massive muscular chest, almost no waist at all, massive muscular hindquarters, and long, spindly, almost cartoonishly thin legs. And, this built-for-speed physique brings up one of the cruelest aspects of horse racing: Thoroughbreds are prone to "break down."
These horses are structured unnaturally, like aliens. Having such a massive, muscular, powerful architecture stilted on such twig-like legs (and getting more massive and twiggier due to constant selective breeding of these traits) is a recipe for disaster. "Breaking down" in horse terms is a rather correct term. Their leg bones break under the stress and force of running, then the horse's weight and thrust breaks the legs down further.
The name Barabaro might come to memory. Barbaro won the Kentucky Derby in 2006 impressively, by a full 6.5 lengths. Hopes were high for a Triple Crown winner. At the Preakness two weeks later, Barabaro broke down. Actually, in his pre-start excitement he broke through the gate to false start. These animals are bred to run and race, they know when it's race time. He was so jacked up and ready to run while in the starting gate, he bucked up, banged his head hard, then literally broke through the gate to false start. Then, after reentering, he started off the race clean before breaking down in front of the main grandstand of viewers. Horse's can break any of their several leg bones. Barbaro broke the cannon, sesamoid, long pastern, and dislocated the fetlock (ankle joint). In other words, he shattered his leg.
When horses break their legs, they're usually put down. As to why, there are lots of reasons, but it comes down to the fact that horses are built for standing and running, especially Thoroughbreds. They are not built for laying down to recuperate, and actually suffer health consequences for not standing. Understandably, a broken leg causes the horse to favor weight to the other legs while standing and this, in turn, can cause other issues. Altogether, the horse suffers.
In Barbaro's case, they tried to rehab him. I think normally he would have been put down on the track in the equine ambulance (the "meat wagon"), but this was Barbaro. The resources were there, he was beloved, and millions had witnessed his injury live. Not trying to save him would have been a public relations nightmare. Putting him down on live TV would have been even worse. There was surgery, then laminitis (inflammation under the hoof) in his opposite good hoof, the result of standing unnaturally. He rallied, then had more setbacks including laminitis in his front hooves. He was in pain, with no way to stand, and then was euthanized in 2007.
!(image)[https://files.peakd.com/file/peakd-hive/crrdlx/23wgoS1v6e2i2gizAqeMeXHf6Zwhz3BTuYMuYNL676tqbPZWwvXUhw7R1J6K4r7DmRj2K.png]
Regarding the money, top studs earn $200 to $400,000 for stud service. A top mare can be bought for $100 to $300,000, then you need the stud service. This is only to breed the foal. This has nothing to do with stabling or training the animals. In other words, it's extremely expensive.
Also regarding the money, there is, of course, the gambling. You might say this is the whole point of horse racing. It's certainly the whole point for breeding Thoroughbreds. It was the whole point for Greyhounds in Florida, before that point was banned.
This year, an estimated $200 million was bet on the Kentucky Derby, the one race alone. $300 million was bet on the races combined. Grok estimated that globally in 2022, horse racing was a $402 billion dollar industry and expects it to grow to $793 billion by 2030.
Those numbers are staggering. But, again, I come back to sinful man. Our love of money is the root of this beautiful evil called horse racing.
I really don't know many scenes more beautiful than a Kentucky horse ranch and a Thoroughbred running across the bluegrass. Add a colt running with his mother, the beauty is staggering. But, underneath that beauty, there is an evil side to horse racing. That side is fueled by sinful man's pride to win and his love of money.
Horse racing is a beautiful evil.


Image sources: https://wikipedia.org, original by me at the track, equine bones at https://www.anatomy-of-the-equine.com/distal-limb-bones.html, the final two images from https://pixabay.com
Note: In the "Can you tell the difference" side-by-side images above, the Thoroughbred was on the left, the Standardbred on the right.
-
 @ d0fbe941:bbce9a00
2025-05-07 02:55:20
@ d0fbe941:bbce9a00
2025-05-07 02:55:20No cenário atual de entretenimento digital, a 119Bet vem ganhando destaque como uma plataforma inovadora e confiável, oferecendo uma experiência completa para jogadores que buscam diversão, emoção e praticidade. Com uma interface moderna, sistema de segurança avançado e uma variedade de jogos envolventes, a 119Bet se consolida como uma excelente opção para quem deseja explorar o mundo dos jogos online com comodidade e segurança.
Uma Plataforma Feita para o Jogador Brasileiro Desde o primeiro acesso, a 119Bet surpreende pela facilidade de navegação e o design adaptado para dispositivos móveis e computadores. A plataforma é totalmente otimizada para garantir uma experiência fluida, seja em smartphones Android, iPhones ou navegadores de desktop. Além disso, o site está disponível em português brasileiro, o que facilita ainda mais a interação dos usuários locais.
O processo de cadastro é simples e rápido, permitindo que novos usuários comecem a jogar em poucos minutos. A 119bettambém se destaca pelo suporte eficiente, com atendimento ao cliente disponível em diversos canais, incluindo chat ao vivo e WhatsApp, garantindo que qualquer dúvida ou problema seja resolvido com agilidade.
Variedade de Jogos para Todos os Gostos A diversidade de jogos é um dos pontos fortes da 119Bet. A plataforma oferece uma ampla seleção que inclui jogos de mesa, cartas, slots temáticos e opções ao vivo com crupiês reais. Tudo é fornecido por desenvolvedores reconhecidos no mercado, o que assegura gráficos de alta qualidade, som envolvente e mecânicas justas.
Os jogos de cartas, como o pôquer e o blackjack, são perfeitos para quem gosta de estratégia e tomada de decisão. Já os slots são indicados para quem busca uma experiência mais dinâmica e visualmente atraente, com temas variados que vão desde mitologia até aventuras futuristas. Para quem gosta de um toque mais realista, as salas ao vivo oferecem uma experiência imersiva e interativa.
Experiência do Jogador: Simples, Segura e Recompensadora A 119Bet foi desenvolvida pensando no conforto e na segurança do jogador. A plataforma utiliza criptografia de dados e tecnologias de proteção contra fraudes para garantir que todas as transações e informações pessoais estejam seguras.
Outro grande atrativo é o sistema de recompensas e promoções. A 119Bet oferece bônus de boas-vindas, rodadas grátis e programas de fidelidade para os jogadores mais frequentes. Tudo isso é estruturado de forma clara, sem complicações, permitindo que o usuário aproveite ao máximo cada benefício.
Além disso, os métodos de pagamento disponíveis incluem opções amplamente utilizadas no Brasil, como PIX, boleto bancário, transferências e carteiras digitais. Os saques são rápidos, e os depósitos caem quase que instantaneamente na conta do jogador.
Conclusão A 119Bet é mais do que uma plataforma de jogos — é um ambiente completo de entretenimento digital, que combina tecnologia, variedade e suporte ao usuário. Com seu compromisso com a segurança, a transparência e a diversão, ela conquista cada vez mais espaço entre os jogadores brasileiros.
Se você está em busca de uma nova experiência online, com jogos envolventes, atendimento de qualidade e ótimas recompensas, a 119Bet é uma escolha certeira. Prepare-se para se divertir com confiança e emoção em cada rodada.
-
 @ c631e267:c2b78d3e
2025-05-02 20:05:22
@ c631e267:c2b78d3e
2025-05-02 20:05:22Du bist recht appetitlich oben anzuschauen, \ doch unten hin die Bestie macht mir Grauen. \ Johann Wolfgang von Goethe
Wie wenig bekömmlich sogenannte «Ultra-Processed Foods» wie Fertiggerichte, abgepackte Snacks oder Softdrinks sind, hat kürzlich eine neue Studie untersucht. Derweil kann Fleisch auch wegen des Einsatzes antimikrobieller Mittel in der Massentierhaltung ein Problem darstellen. Internationale Bemühungen, diesen Gebrauch zu reduzieren, um die Antibiotikaresistenz bei Menschen einzudämmen, sind nun möglicherweise gefährdet.
Leider ist Politik oft mindestens genauso unappetitlich und ungesund wie diverse Lebensmittel. Die «Corona-Zeit» und ihre Auswirkungen sind ein beredtes Beispiel. Der Thüringer Landtag diskutiert gerade den Entwurf eines «Coronamaßnahmen-Unrechtsbereinigungsgesetzes» und das kanadische Gesundheitsministerium versucht, tausende Entschädigungsanträge wegen Impfnebenwirkungen mit dem Budget von 75 Millionen Dollar unter einen Hut zu bekommen. In den USA soll die Zulassung von Covid-«Impfstoffen» überdacht werden, während man sich mit China um die Herkunft des Virus streitet.
Wo Corona-Verbrecher von Medien und Justiz gedeckt werden, verfolgt man Aufklärer und Aufdecker mit aller Härte. Der Anwalt und Mitbegründer des Corona-Ausschusses Reiner Fuellmich, der seit Oktober 2023 in Untersuchungshaft sitzt, wurde letzte Woche zu drei Jahren und neun Monaten verurteilt – wegen Veruntreuung. Am Mittwoch teilte der von vielen Impfschadensprozessen bekannte Anwalt Tobias Ulbrich mit, dass er vom Staatsschutz verfolgt wird und sich daher künftig nicht mehr öffentlich äußern werde.
Von der kommenden deutschen Bundesregierung aus Wählerbetrügern, Transatlantikern, Corona-Hardlinern und Russenhassern kann unmöglich eine Verbesserung erwartet werden. Nina Warken beispielsweise, die das Ressort Gesundheit übernehmen soll, diffamierte Maßnahmenkritiker als «Coronaleugner» und forderte eine Impfpflicht, da die wundersamen Injektionen angeblich «nachweislich helfen». Laut dem designierten Außenminister Johann Wadephul wird Russland «für uns immer der Feind» bleiben. Deswegen will er die Ukraine «nicht verlieren lassen» und sieht die Bevölkerung hinter sich, solange nicht deutsche Soldaten dort sterben könnten.
Eine wichtige Personalie ist auch die des künftigen Regierungssprechers. Wenngleich Hebestreit an Arroganz schwer zu überbieten sein wird, dürfte sich die Art der Kommunikation mit Stefan Kornelius in der Sache kaum ändern. Der Politikchef der Süddeutschen Zeitung «prägte den Meinungsjournalismus der SZ» und schrieb «in dieser Rolle auch für die Titel der Tamedia». Allerdings ist, anders als noch vor zehn Jahren, die Einbindung von Journalisten in Thinktanks wie die Deutsche Atlantische Gesellschaft (DAG) ja heute eher eine Empfehlung als ein Problem.
Ungesund ist definitiv auch die totale Digitalisierung, nicht nur im Gesundheitswesen. Lauterbachs Abschiedsgeschenk, die «abgesicherte» elektronische Patientenakte (ePA) ist völlig überraschenderweise direkt nach dem Bundesstart erneut gehackt worden. Norbert Häring kommentiert angesichts der Datenlecks, wer die ePA nicht abwähle, könne seine Gesundheitsdaten ebensogut auf Facebook posten.
Dass die staatlichen Kontrolleure so wenig auf freie Software und dezentrale Lösungen setzen, verdeutlicht die eigentlichen Intentionen hinter der Digitalisierungswut. Um Sicherheit und Souveränität geht es ihnen jedenfalls nicht – sonst gäbe es zum Beispiel mehr Unterstützung für Bitcoin und für Initiativen wie die der Spar-Supermärkte in der Schweiz.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ c3b2802b:4850599c
2025-05-07 11:26:36
@ c3b2802b:4850599c
2025-05-07 11:26:36Heute, am 9. Mai 2025 – genau 80 Jahre nach dem Ende des Zweiten Weltkriegs, der 60 Millionen Menschen das Leben kostete, darunter 27 Millionen Sowjetbürgern, erheben wir, die Bürgerinnen und Bürger Europas, unsere Stimmen! Wir schämen uns für unsere Regierungen und die EU, die die Lehren des 20. Jahrhunderts nicht gelernt haben. Die EU, einst als Friedensprojekt gedacht, wurde pervertiert und hat damit den Wesenskern Europas verraten! Wir, die Bürger Europas, nehmen darum heute, am 9. Mai, unsere Geschicke und unsere Geschichte selbst in die Hand. Wir erklären die EU für gescheitert. Wir beginnen mit Bürger-Diplomatie und verweigern uns dem geplanten Krieg gegen Russland! Wir erkennen die Mitverantwortung des „Westens“, der europäischen Regierungen und der EU an diesem Konflikt an.
Wir, die Bürger Europas, treten mit dem European Peace Project der schamlosen Heuchlerei und den Lügen entgegen, die heute – am Europatag – auf offiziellen Festakten und in öffentlichen Sendern verbreitet werden.
Wir strecken den Bürgerinnen und Bürgern der Ukraine und Russlands die Hand aus. Ihr gehört zur europäischen Familie, und wir sind überzeugt, dass wir gemeinsam ein friedliches Zusammenleben auf unserem Kontinent organisieren können.
Wir haben die Bilder der Soldatenfriedhöfe vor Augen – von Wolgograd über Riga bis Lothringen. Wir sehen die frischen Gräber, die dieser sinnlose Krieg in der Ukraine und in Russland hinterlassen hat. Während die meisten EU-Regierungen und Verantwortlichen für den Krieg hetzen und verdrängen, was Krieg für die Bevölkerung bedeutet, haben wir die Lektion des letzten Jahrhunderts gelernt: Europa heißt „Nie wieder Krieg!“
Wir erinnern uns an die europäischen Aufbauleistungen des letzten Jahrhunderts und an die Versprechen von 1989 nach der friedlichen Revolution. Wir fordern ein europäisch-russisches Jugendwerk nach dem Vorbild des deutsch-französischen Jugendwerks von 1963, das die „Erbfeindschaft“ zwischen Deutschland und Frankreich beendet hat. Wir fordern ein Ende der Sanktionen und den Wiederaufbau der Nord Stream II-Pipeline. Wir weigern uns, unsere Steuergelder für Rüstung und Militarisierung zu verschwenden, auf Kosten von Sozialstandards und Infrastruktur. Im Rahmen einer OSZE-Friedenskonferenz fordern wir die Schaffung einer europäischen Sicherheitsarchitektur mit und nicht gegen Russland, wie in der Charta von Paris von 1990 festgelegt. Wir fordern ein neutrales, von den USA emanzipiertes Europa, das eine vermittelnde Rolle in einer multipolaren Welt einnimmt. Unser Europa ist post-kolonial und post-imperial.
Wir, die Bürger Europas, erklären diesen Krieg hiermit für beendet! Wir machen bei den Kriegsspielen nicht mit. Wir machen aus unseren Männern und Söhnen keine Soldaten, aus unseren Töchtern keine Schwestern im Lazarett und aus unseren Ländern keine Schlachtfelder.
Wir bieten an, sofort eine Abordnung europäischer Bürgerinnen und Bürger nach Kiew und Moskau zu entsenden, um den Dialog zu beginnen. Wir werden nicht länger zusehen, wie unsere Zukunft und die unserer Kinder auf dem Altar der Machtpolitik geopfert wird.
Es lebe Europa, es lebe der Friede, es lebe die Freiheit
Auf der Webseite der Initiative oder in einem Gespräch mit Ulrike Guérot können Sie, liebe Leser, weitere Möglichkeiten erfahren, diese Friedensinitiative zu stärken! Danke an die IntiatorInnen und die bislang 15.000 Menschen, die das mitgestalten werden.
Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
-
 @ d0fbe941:bbce9a00
2025-05-07 02:54:44
@ d0fbe941:bbce9a00
2025-05-07 02:54:44Com o avanço da tecnologia e a popularização dos jogos digitais, plataformas de entretenimento online têm ganhado cada vez mais destaque no Brasil. Entre as opções que vêm conquistando o público, a 355Bet surge como uma alternativa moderna, segura e recheada de possibilidades para quem busca diversão e recompensas reais. Este artigo apresenta um panorama completo sobre a 355Bet, destacando seus principais diferenciais, os jogos disponíveis e a experiência dos jogadores brasileiros na plataforma.
Plataforma moderna e intuitiva A 355Bet foi desenvolvida com foco na usabilidade e na acessibilidade. Seu design responsivo permite que os usuários acessem todas as funcionalidades tanto pelo computador quanto por dispositivos móveis, sem comprometer a qualidade da navegação. A interface é limpa, organizada e intuitiva, facilitando a localização de jogos, promoções e opções de suporte ao cliente.
A segurança é outro ponto de destaque. A plataforma utiliza tecnologia de criptografia de ponta para garantir a proteção dos dados dos usuários, além de oferecer métodos de pagamento confiáveis e populares entre os brasileiros, como PIX, boleto bancário e carteiras digitais.
Variedade de jogos para todos os gostos Na 355bet, a diversidade de opções é um dos grandes atrativos. Os jogadores encontram uma ampla seleção de jogos, incluindo:
Slots (caça-níqueis): São dezenas de títulos temáticos, com gráficos envolventes e diferentes níveis de volatilidade. Ideais para quem busca diversão rápida e a chance de obter bons prêmios com pequenas apostas.
Jogos de mesa: Para os fãs de estratégias, há opções como roleta, blackjack e bacará, todos disponíveis em versões digitais com gráficos de alta definição.
Jogos ao vivo: Uma das grandes sensações da plataforma, os jogos com crupiês reais oferecem uma experiência imersiva, com transmissão em tempo real e interação com outros jogadores, elevando o nível de realismo e emoção.
Além disso, a 355Bet está sempre atualizando seu catálogo, trazendo novidades semanais e parcerias com provedores renomados da indústria de entretenimento digital.
Experiência do jogador brasileiro A experiência do usuário é prioridade na 355Bet. A plataforma oferece um atendimento ao cliente eficiente, com suporte em português disponível 24 horas por dia via chat ao vivo, e-mail ou WhatsApp. O processo de cadastro é simples e rápido, permitindo que novos jogadores comecem a se divertir em poucos minutos.
Outro ponto positivo são as promoções exclusivas para brasileiros. Bônus de boas-vindas, ofertas semanais, torneios com prêmios em dinheiro e programas de fidelidade tornam a jornada do jogador ainda mais recompensadora.
Jogadores relatam que a navegação fluida, os pagamentos ágeis e a diversidade de jogos tornam a 355Bet uma das plataformas mais completas do mercado. Seja para iniciantes ou experientes, a plataforma oferece uma experiência equilibrada entre diversão e oportunidade de ganhos.
Conclusão A 355Bet chegou ao Brasil para redefinir a forma como os jogadores interagem com o entretenimento digital. Com uma plataforma segura, acessível e repleta de jogos emocionantes, ela se posiciona como uma das principais escolhas para quem busca emoção, variedade e uma experiência de alta qualidade. Se você está em busca de uma nova forma de se divertir online, vale a pena conhecer tudo o que a 355Bet tem a oferecer.
-
 @ 7e538978:a5987ab6
2025-05-07 10:25:30
@ 7e538978:a5987ab6
2025-05-07 10:25:30Across Switzerland, customers at SPAR supermarkets are now able to pay for their groceries using Lightning on Bitcoin — a step towards everyday Bitcoin adoption. This rollout was led by DFX, a Bitcoin services company focused on onboarding businesses and individuals to Bitcoin. Behind the scenes LNbits plays a key role.
 ## Lightning at the Checkout
## Lightning at the CheckoutSPAR’s approach is simple: at the till, customers can scan a static QR code to pay in Bitcoin using the Lightning Network. Each checkout in each participating store has its own unique LNURL address — a reusable QR code designed for fast, low-friction Lightning payments.
To manage these LNURLs, DFX leverages LNbits. Using the LNbits Pay Links extension, DFX generates LNURLs for each till across the network of participating SPAR locations. The result is a robust, reliable setup that works at scale. Store staff do not interact with LNbits directly — instead, DFX manages the backend, ensuring each till has a dedicated LNURL without operational overhead for SPAR employees.
At SPAR we use static QR codes that meet the LNURL standard. Therefore we use LNbits. Each checkout has its own personal LNURL address which we generate with LNbits.
— Cyrill Thommen, CEO of DFX.Swiss— Cyrill Thommen, CEO of DFX.Swiss
 ## LNbits in Action
## LNbits in ActionLNbits provided DFX with a modular, open-source solution that allows them to build only what they need, without locking into a rigid platform. For instance, DFX built custom monitoring around payment events using the LNbits API, while keeping full control over wallet infrastructure.
The ability to generate and manage LNURLs through the LNbits API, while layering additional monitoring and business logic on top, made LNbits a practical choice.
DFX’s setup highlights how open source software, Bitcoin and purpose-built tools can underpin enterprise-grade deployments. The system works reliably — without introducing friction for customers or staff.
Bitcoin in the Real World
Switzerland is already one of Europe’s most Bitcoin-friendly environments, with over 1,000 businesses accepting Bitcoin. But SPAR’s implementation is noteworthy for its scale and practicality: everyday purchases, completed with Bitcoin, at a national supermarket chain.
LNbits' flexible architecture, API-first design, and plug-in system make it well suited to precisely this kind of adoption.
As more retailers explore Lightning integration, SPAR’s rollout sets a precedent — showing how modular, open-source tools like LNbits can bring Bitcoin into daily life, seamlessly.

-
 @ 502ab02a:a2860397
2025-05-07 01:08:58
@ 502ab02a:a2860397
2025-05-07 01:08:58สัปดาห์นี้ถือว่าเป็นเบรคคั่นพักผ่อนแก้เครียดนิดหน่อยแล้วกันครับ เรามาเล่าย้อนอดีตกันนิดหน่อย เหมือนสตาร์วอส์ที่ฉายภาค 4-5-6 แล้วย้อนไป 1-2-3 ฮาๆๆๆ
เคยได้ยินคำว่า Nuremberg Trials ไหมครับ ย้อนความนิดนึงว่า Nuremberg (Nürnberg อ่านว่า เนือร์นแบร์ก) คือชื่อเมืองในเยอรมนีที่เคยเป็นเวทีพิจารณาคดีประวัติศาสตร์หลังสงครามโลกครั้งที่ 2
“Nuremberg Trials” คือการไต่สวนผู้มีส่วนเกี่ยวข้องกับ อาชญากรรมสงครามของนาซีเยอรมัน หลังสงครามโลกครั้งที่ 2 ในปี 1945–46 พันธมิตรผู้ชนะสงครามได้จับตัวผู้นำนาซี นักการเมือง หมอ นักวิทยาศาสตร์ มาขึ้นศาล ข้อหาของพวกเขาไม่ได้แค่ฆ่าคน แต่รวมถึงการละเมิดศีลธรรมมนุษย์ขั้นพื้นฐาน อย่างการทดลองทางการแพทย์กับนักโทษ โดยไม่มีการขอความยินยอม
จากการไต่สวนนี้ จึงเกิดหลักจริยธรรมที่ชื่อว่า “Nuremberg Code” ซึ่งกลายเป็นรากฐานของการทดลองทางการแพทย์ยุคใหม่ หัวใจของโค้ดนี้คือคำว่า “Informed Consent” แปลว่า ถ้าจะทำอะไรกับร่างกายใคร ต้องได้รับความยินยอมจากเขาอย่างเต็มใจ และมีข้อมูลครบถ้วน นี่แหละ คือบทเรียนจากบาดแผลของสงครามโลก
แต่แล้ว...ในปี 2020 โลกก็เข้าสู่ยุคที่ใครบางคนบอกว่า “ต้องเชื่อผู้เชี่ยวชาญ” ใครกังวล = คนไม่รักสังคม ใครถามเยอะ = คนต่อต้านวิทยาศาสตร์ การยินยอมโดยสมัครใจ เริ่มกลายเป็นแค่คำเชิงสัญลักษณ์
ในช่วงหลังนี้เราอาจจะได้ยินข่าวหรือทฤษฎีในอินเตอร์เนทเกี่ยวกับคำว่า Nuremberg 2.0 กันนะครับ เพราะเริ่มผุดขึ้นตามกระทู้เงียบ ๆ คลิปใต้ดิน และเวทีเสวนาแปลก ๆ ที่ไม่มีใครอยากอ้างชื่อบนเวที TED Talk ซึ่ง กลุ่มที่ใช้คำนี้มักจะหมายถึงความต้องการให้มีการ “ไต่สวน” หรือ “เอาผิด” กับนักการเมือง นักวิทยาศาสตร์ แพทย์ หรือองค์กรที่เกี่ยวข้องกับ การออกคำสั่ง การบังคับ การเซ็นเซอร์ข้อมูลที่ขัดแย้งกับแนวทางรัฐ การเผยแพร่ข้อมูลโดยไม่โปร่งใส พวกเขามองว่า นโยบายเหล่านั้นละเมิดสิทธิเสรีภาพของประชาชนในระดับที่เปรียบได้กับ “อาชญากรรมต่อมนุษยชาติ” จึงเสนอแนวคิด “Nuremberg 2.0”
พวกเขาไม่ได้เรียกร้องแค่ความโปร่งใส แต่เขาอยากเห็นการทบทวน ว่าใครกันแน่ที่ละเมิดหลักจริยธรรมที่โลกเคยตกลงกันไว้เมื่อ 80 ปีก่อน
Nuremberg คือการไต่สวนคนที่ใช้อำนาจรัฐฆ่าคนอย่างจงใจ Nuremberg 2.0 คือคำเตือนว่า “การใช้ความกลัวครอบงำเสรีภาพ” อาจไม่ต่างกันนัก
ทีนี้เคยสงสัยไหม แล้วมันเกี่ยวอะไรกับอาหาร?
เพราะจากวิกฤตโรคระบาด เราเริ่มเห็น “วิทยาศาสตร์แบบผูกขาด” คุมเกมส์ บริษัทเทคโนโลยีเริ่มเข้ามาทำอาหาร ชื่อใหม่ของเนื้อสเต๊กกลายเป็น “โปรตีนทางเลือก” อาหารจากแล็บกลายเป็น “ทางรอดของโลก” สารเคมีอัดลงไปแทนเนื้อจริง ๆ แต่มีฉลากติดว่า "รักษ์โลก ปลอดภัย ยั่งยืน"
แต่ถ้ามองให้ลึกลงไปอีกนิด บางกลุ่มคนกลับเริ่มเห็นอะไรบางอย่างที่ขนลุกกว่า เพราะมันคือ “ระบบควบคุมสุขภาพ” ที่อาศัย “ความกลัว” เป็นหัวเชื้อ และ “วิทยาศาสตร์แบบผูกขาด” เป็นกลไก
จากนั้น…ทุกอย่างก็จะถูกเสิร์ฟอย่างสวยงามในรูปแบบ "นวัตกรรมเพื่ออนาคต" ไม่ว่าจะเป็นอาหารเสริมชนิดใหม่ เนื้อสัตว์ปลูกในแล็บ หรืออาหารที่ไม่ต้องเคี้ยว
ลองคิดเล่น ๆครับ ถ้าสารอาหารถูกควบคุมได้ เหมือนที่เราเคยถูกบังคับกับบางอย่างได้ล่ะ? วันหนึ่ง เราอาจถูกขอให้ "กิน" ในสิ่งที่ระบบสุขภาพอนาคตเขาบอกว่าดี แล้วถ้าเฮียบอกว่าไม่อยากกิน...เขาอาจไม่ห้าม แต่ App สุขภาพจะเตือนว่า “คุณมีพฤติกรรมเสี่ยงต่อโลกใบนี้” แต้มเครดิตจะสุขภาพจะลดลงและส่วนลดข้าวกล่องเนื้อจากจุลินทรีย์จะไม่เข้าบัญชีเฮียอีกเลย
ใช่…มันไม่เหมือนการบังคับ แต่มันคือการสร้าง “ระบบทางเดียว” ที่ทำให้คนที่อยากเดินออกนอกแถว เหมือนเดินลงเหว
Nuremberg 2.0 จึงไม่ใช่แค่เรื่องของอดีตหรือโรคระบาด แต่มันเป็นกระจกที่สะท้อนว่า “ถ้าเราไม่เรียนรู้จากประวัติศาสตร์ เราอาจกินซ้ำรอยมันเข้าไปในมื้อเย็น”
อนาคตของอาหารอาจไม่ได้อยู่ในจาน แต่อยู่ในนโยบาย อยู่ในบริษัทที่ผลิตโปรตีนจากอากาศ อยู่ในทุนที่ซื้อนักวิทยาศาสตร์ไว้ทั้งวงการ และถ้าเราหลับตาอีกครั้ง หลายคนก็กลัวว่า...บทไต่สวน Nuremberg รอบใหม่ อาจไม่สามารถเกิดขึ้นอีกต่อไป เพราะคราวนี้ คนร้ายจะไม่ได้ถือปืน แต่อาจถือใบรับรองโภชนาการระดับโลกในมือแทน
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 088436cd:9d2646cc
2025-05-01 21:01:55
@ 088436cd:9d2646cc
2025-05-01 21:01:55The arrival of the coronavirus brought not only illness and death but also fear and panic. In such an environment of uncertainty, people have naturally stocked up on necessities, not knowing when things will return to normal.
Retail shelves have been cleared out, and even online suppliers like Amazon and Walmart are out of stock for some items. Independent sellers on these e-commerce platforms have had to fill the gap. With the huge increase in demand, they have found that their inventory has skyrocketed in value.
Many in need of these items (e.g. toilet paper, hand sanitizer and masks) balk at the new prices. They feel they are being taken advantage of in a time of need and call for intervention by the government to lower prices. The government has heeded that call, labeling the independent sellers as "price gougers" and threatening sanctions if they don't lower their prices. Amazon has suspended seller accounts and law enforcement at all levels have threatened to prosecute. Prices have dropped as a result and at first glance this seems like a victory for fair play. But, we will have to dig deeper to understand the unseen consequences of this intervention.
We must look at the economics of the situation, how supply and demand result in a price and how that price acts as a signal that goes out to everyone, informing them of underlying conditions in the economy and helping coordinate their actions.
It all started with a rise in demand. Given a fixed supply (e.g., the limited stock on shelves and in warehouses), an increase in demand inevitably leads to higher prices. Most people are familiar with this phenomenon, such as paying more for airline tickets during holidays or surge pricing for rides.
Higher prices discourage less critical uses of scarce resources. For example, you might not pay $1,000 for a plane ticket to visit your aunt if you can get one for $100 the following week, but someone else might pay that price to visit a dying relative. They value that plane seat more than you.
*** During the crisis, demand surged and their shelves emptied even though
However, retail outlets have not raised prices. They have kept them low, so the low-value uses of things like toilet paper, masks and hand sanitizer has continued. Often, this "use" just takes the form of hoarding. At everyday low prices, it makes sense to buy hundreds of rolls and bottles. You know you will use them eventually, so why not stock up? And, with all those extra supplies in the closet and basement, you don't need to change your behavior much. You don't have to ration your use.
At the low prices, these scarce resources got bought up faster and faster until there was simply none left. The reality of the situation became painfully clear to those who didn't panic and got to the store late: You have no toilet paper and you're not going to any time soon.
However, if prices had been allowed to rise, a number of effects would have taken place that would have coordinated the behavior of everyone so that valuable resources would not have been wasted or hoarded, and everyone could have had access to what they needed.
On the demand side, if prices had been allowed to rise, people would have begun to self-ration. You might leave those extra plies on the roll next time if you know they will cost ten times as much to replace. Or, you might choose to clean up a spill with a rag rather than disposable tissue. Most importantly, you won't hoard as much. That 50th bottle of hand sanitizer might just not be worth it at the new, high price. You'll leave it on the shelf for someone else who may have none.
On the supply side, higher prices would have incentivized people to offer up more of their stockpiles for sale. If you have a pallet full of toilet paper in your basement and all of the sudden they are worth $15 per roll, you might just list a few online. But, if it is illegal to do so, you probably won't.
Imagine you run a business installing insulation and have a few thousand respirator masks on hand for your employees. During a pandemic, it is much more important that people breathe filtered air than that insulation get installed, and that fact is reflected in higher prices. You will sell your extra masks at the higher price rather than store them for future insulation jobs, and the scarce resource will be put to its most important use.
Producers of hand sanitizer would go into overdrive if prices were allowed to rise. They would pay their employees overtime, hire new ones, and pay a premium for their supplies, making sure their raw materials don't go to less important uses.
These kinds of coordinated actions all across the economy would be impossible without real prices to guide them. How do you know if it makes sense to spend an extra $10k bringing a thousand masks to market unless you know you can get more than $10 per mask? If the price is kept artificially low, you simply can't do it. The money just isn't there.
These are the immediate effects of a price change, but incredibly, price changes also coordinate people's actions across space and time.
Across space, there are different supply and demand conditions in different places, and thus prices are not uniform. We know some places are real "hot spots" for the virus, while others are mostly unaffected. High demand in the hot spots leads to higher prices there, which attracts more of the resource to those areas. Boxes and boxes of essential items would pour in where they are needed most from where they are needed least, but only if prices were allowed to adjust freely.
This would be accomplished by individuals and businesses buying low in the unaffected areas, selling high in the hot spots and subtracting their labor and transportation costs from the difference. Producers of new supply would know exactly where it is most needed and ship to the high-demand, high-price areas first. The effect of these actions is to increase prices in the low demand areas and reduce them in the high demand areas. People in the low demand areas will start to self-ration more, reflecting the reality of their neighbors, and people in the hotspots will get some relief.
However, by artificially suppressing prices in the hot spot, people there will simply buy up the available supply and run out, and it will be cost prohibitive to bring in new supply from low-demand areas.
Prices coordinate economic actions across time as well. Just as entrepreneurs and businesses can profit by transporting scarce necessities from low-demand to high-demand areas, they can also profit by buying in low-demand times and storing their merchandise for when it is needed most.
Just as allowing prices to freely adjust in one area relative to another will send all the right signals for the optimal use of a scarce resource, allowing prices to freely adjust over time will do the same.
When an entrepreneur buys up resources during low-demand times in anticipation of a crisis, she restricts supply ahead of the crisis, which leads to a price increase. She effectively bids up the price. The change in price affects consumers and producers in all the ways mentioned above. Consumers self-ration more, and producers bring more of the resource to market.
Our entrepreneur has done a truly incredible thing. She has predicted the future, and by so doing has caused every individual in the economy to prepare for a shortage they don't even know is coming! And, by discouraging consumption and encouraging production ahead of time, she blunts the impact the crisis will have. There will be more of the resource to go around when it is needed most.
On top of this, our entrepreneur still has her stockpile she saved back when everyone else was blithely using it up. She can now further mitigate the damage of the crisis by selling her stock during the worst of it, when people are most desperate for relief. She will know when this is because the price will tell her, but only if it is allowed to adjust freely. When the price is at its highest is when people need the resource the most, and those willing to pay will not waste it or hoard it. They will put it to its highest valued use.
The economy is like a big bus we are all riding in, going down a road with many twists and turns. Just as it is difficult to see into the future, it is difficult to see out the bus windows at the road ahead.
On the dashboard, we don't have a speedometer or fuel gauge. Instead we have all the prices for everything in the economy. Prices are what tell us the condition of the bus and the road. They tell us everything. Without them, we are blind.
Good times are a smooth road. Consumer prices and interest rates are low, investment returns are steady. We hit the gas and go fast. But, the road is not always straight and smooth. Sometimes there are sharp turns and rough patches. Successful entrepreneurs are the ones who can see what is coming better than everyone else. They are our navigators.
When they buy up scarce resources ahead of a crisis, they are hitting the brakes and slowing us down. When they divert resources from one area to another, they are steering us onto a smoother path. By their actions in the market, they adjust the prices on our dashboard to reflect the conditions of the road ahead, so we can prepare for, navigate and get through the inevitable difficulties we will face.
Interfering with the dashboard by imposing price floors or price caps doesn't change the conditions of the road (the number of toilet paper rolls in existence hasn't changed). All it does is distort our perception of those conditions. We think the road is still smooth--our heavy foot stomping the gas--as we crash onto a rocky dirt road at 80 miles per hour (empty shelves at the store for weeks on end).
Supply, demand and prices are laws of nature. All of this is just how things work. It isn't right or wrong in a moral sense. Price caps lead to waste, shortages and hoarding as surely as water flows downhill. The opposite--allowing prices to adjust freely--leads to conservation of scarce resources and their being put to their highest valued use. And yes, it leads to profits for the entrepreneurs who were able to correctly predict future conditions, and losses for those who weren't.
Is it fair that they should collect these profits? On the one hand, anyone could have stocked up on toilet paper, hand sanitizer and face masks at any time before the crisis, so we all had a fair chance to get the supplies cheaply. On the other hand, it just feels wrong that some should profit so much at a time when there is so much need.
Our instinct in the moment is to see the entrepreneur as a villain, greedy "price gouger". But we don't see the long chain of economic consequences the led to the situation we feel is unfair.
If it weren't for anti-price-gouging laws, the major retailers would have raised their prices long before the crisis became acute. When they saw demand outstrip supply, they would have raised prices, not by 100 fold, but gradually and long before anyone knew how serious things would have become. Late comers would have had to pay more, but at least there would be something left on the shelf.
As an entrepreneur, why take risks trying to anticipate the future if you can't reap the reward when you are right? Instead of letting instead of letting entrepreneurs--our navigators--guide us, we are punishing and vilifying them, trying to force prices to reflect a reality that simply doesn't exist.
In a crisis, more than any other time, prices must be allowed to fluctuate. To do otherwise is to blind ourselves at a time when danger and uncertainty abound. It is economic suicide.
In a crisis, there is great need, and the way to meet that need is not by pretending it's not there, by forcing prices to reflect a world where there isn't need. They way to meet the need is the same it has always been, through charity.
If the people in government want to help, the best way for the to do so is to be charitable and reduce their taxes and fees as much as possible, ideally to zero in a time of crisis. Amazon, for example, could instantly reduce the price of all crisis related necessities by 20% if they waived their fee. This would allow for more uses by more people of these scarce supplies as hoarders release their stockpiles on to the market, knowing they can get 20% more for their stock. Governments could reduce or eliminate their tax burden on high-demand, crisis-related items and all the factors that go into their production, with the same effect: a reduction in prices and expansion of supply. All of us, including the successful entrepreneurs and the wealthy for whom high prices are not a great burden, could donate to relief efforts.
These ideas are not new or untested. This is core micro economics. It has been taught for hundreds of years in universities the world over. The fact that every crisis that comes along stirs up ire against entrepreneurs indicates not that the economics is wrong, but that we have a strong visceral reaction against what we perceive to be unfairness. This is as it should be. Unfairness is wrong and the anger it stirs in us should compel us to right the wrong. Our anger itself isn't wrong, it's just misplaced.
Entrepreneurs didn't cause the prices to rise. Our reaction to a virus did that. We saw a serious threat and an uncertain future and followed our natural impulse to hoard. Because prices at major retail suppliers didn't rise, that impulse ran rampant and we cleared the shelves until there was nothing left. We ran the bus right off the road and them blamed the entrepreneurs for showing us the reality of our situation, for shaking us out of the fantasy of low prices.
All of this is not to say that entrepreneurs are high-minded public servants. They are just doing their job. Staking your money on an uncertain future is a risky business. There are big risks and big rewards. Most entrepreneurs just scrape by or lose their capital in failed ventures.
However, the ones that get it right must be allowed to keep their profits, or else no one will try and we'll all be driving blind. We need our navigators. It doesn't even matter if they know all the positive effects they are having on the rest of us and the economy as a whole. So long as they are buying low and selling high--so long as they are doing their job--they will be guiding the rest of us through the good times and the bad, down the open road and through the rough spots.
-
 @ 90c656ff:9383fd4e
2025-05-06 14:10:48
@ 90c656ff:9383fd4e
2025-05-06 14:10:48Bitcoin has been gaining increasing acceptance as a means of payment, evolving from being just a digital investment asset to becoming a viable alternative to traditional currencies. Today, many companies around the world already accept Bitcoin, providing consumers with greater financial freedom and reducing reliance on traditional banking intermediaries.
- Global companies that accept Bitcoin
Over the years, several well-known companies have begun accepting Bitcoin, recognizing its benefits such as security, transparency, and low transaction fees. Among the most prominent are:
01 - Microsoft: The tech giant allows users to add funds to their Microsoft accounts using Bitcoin. This enables the purchase of digital content such as games, apps, and software available in the Microsoft Store. 02 - Overstock: One of the largest online retailers that accepts Bitcoin for the purchase of furniture, electronics, and home goods. Overstock was an early adopter, signaling a strong commitment to financial innovation. 03 - AT&T: The U.S. telecommunications company was the first in its industry to accept Bitcoin payments, giving customers the option to pay their bills with cryptocurrency through BitPay. 04 - Twitch: While Twitch does not natively support Bitcoin donations or payments, many streamers use third-party services like NOWPayments, Streamlabs (with Coinbase integration), or Plisio to accept crypto tips and donations. This opens a path for Bitcoin support through external platforms, especially within the content creator community. 05 - Namecheap: A leading domain registrar and web hosting provider that accepts Bitcoin for domain registration and hosting services, showcasing Bitcoin’s usefulness in the digital economy.
- Small businesses and local commerce
Beyond large corporations, a growing number of small businesses and local merchants are embracing Bitcoin, particularly in cities that are becoming hubs for digital innovation.
01 - Restaurants and cafés: In cities like Lisbon, London, and New York, several cafés and eateries accept Bitcoin as payment, attracting tech-savvy customers. 02 - Hotels and tourism: Certain hotel chains and travel platforms now accept Bitcoin, simplifying bookings and removing the need for currency exchange for international travelers. 03 - Online stores: Many small e-commerce businesses offer Bitcoin as a payment option or even operate exclusively using cryptocurrency, benefiting from borderless, fast transactions.
- Advantages for businesses and consumers
The growing acceptance of Bitcoin is largely driven by its advantages:
01 - Lower transaction fees: Businesses can reduce costs associated with credit card fees and payment processors. 02 - No intermediaries: Direct peer-to-peer payments cut down on bureaucracy and reduce fraud risks. 03 - Global access: Bitcoin allows for cross-border payments without the need for currency exchange, ideal for international transactions.
In summary, the adoption of Bitcoin as a means of payment continues to expand, with companies of all sizes recognizing its strategic value. From large enterprises to independent creators and local shops, Bitcoin is gradually becoming a more practical and accepted financial tool. While challenges such as volatility and regulatory uncertainty remain, the broader trend points toward a future where paying with Bitcoin could be a common part of everyday life.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ 90c656ff:9383fd4e
2025-05-06 13:41:50
@ 90c656ff:9383fd4e
2025-05-06 13:41:50Bitcoin was created to offer a secure and decentralized alternative to traditional money, enabling financial transactions without the need for intermediaries. DeFi, on the other hand, emerged as an expansion of this concept, proposing decentralized financial services such as lending, exchanges, and yield generation. However, despite its promises of innovation, DeFi carries numerous risks, making it a dangerous bet for those who value the security of their Bitcoin.
What is DeFi?
DeFi refers to a set of financial applications that operate without the intermediation of banks or traditional institutions. These platforms use smart contracts to automate transactions, allowing anyone to access financial services without relying on third parties. In theory, DeFi promises greater financial freedom, but in practice it is full of risks, scams, and technical vulnerabilities that can compromise users' funds.
- The risks of DeFi for Bitcoin holders
Bitcoin is the most secure digital currency in the world, protected by a decentralized and censorship-resistant network. Unlike DeFi, which is still in an experimental phase and has already suffered numerous attacks, Bitcoin remains solid and reliable. When someone places Bitcoin in DeFi platforms, they give up the security of direct custody and trust weaker systems.
The main risks include:
01 - Hackers and code flaws: Smart contracts are written by programmers and may contain bugs that allow massive thefts. Over the years, billions of dollars have been lost due to vulnerabilities in DeFi platforms. 02 - Liquidation risks: Many DeFi applications operate on collateralization systems, where users lock Bitcoin to obtain loans. If the market becomes volatile, those Bitcoins can be liquidated at lower-than-expected prices, causing irreversible losses. 03 - Scams and rug pulls: DeFi is full of shady projects where creators vanish with users’ funds. Without regulation and without guarantees, those who deposit Bitcoin in these platforms may never recover their funds.
- Keeping Bitcoin safe is the best choice
Bitcoin was created to be self-custodied, meaning each user should have direct control over their funds without relying on third parties. By sending Bitcoin to DeFi platforms, that security is lost and the asset is exposed to unnecessary risks. The best way to protect Bitcoin is to store it in a secure wallet, preferably offline (cold storage), avoiding any exposure to smart contracts or vulnerable systems.
In summary, DeFi may seem innovative, but the risks far outweigh the potential benefits—especially for those who value Bitcoin's security. Instead of risking losing funds on insecure platforms, the wisest choice is to keep Bitcoin safely stored, ensuring its long-term preservation. While Bitcoin continues to be the best digital store of value in the world, DeFi remains an unstable and dangerous environment where few win and many end up losing.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ c631e267:c2b78d3e
2025-04-25 20:06:24
@ c631e267:c2b78d3e
2025-04-25 20:06:24Die Wahrheit verletzt tiefer als jede Beleidigung. \ Marquis de Sade
Sagen Sie niemals «Terroristin B.», «Schwachkopf H.», «korrupter Drecksack S.» oder «Meinungsfreiheitshasserin F.» und verkneifen Sie sich Memes, denn so etwas könnte Ihnen als Beleidigung oder Verleumdung ausgelegt werden und rechtliche Konsequenzen haben. Auch mit einer Frau M.-A. S.-Z. ist in dieser Beziehung nicht zu spaßen, sie gehört zu den Top-Anzeigenstellern.
«Politikerbeleidigung» als Straftatbestand wurde 2021 im Kampf gegen «Rechtsextremismus und Hasskriminalität» in Deutschland eingeführt, damals noch unter der Regierung Merkel. Im Gesetz nicht festgehalten ist die Unterscheidung zwischen schlechter Hetze und guter Hetze – trotzdem ist das gängige Praxis, wie der Titel fast schon nahelegt.
So dürfen Sie als Politikerin heute den Tesla als «Nazi-Auto» bezeichnen und dies ausdrücklich auf den Firmengründer Elon Musk und dessen «rechtsextreme Positionen» beziehen, welche Sie nicht einmal belegen müssen. [1] Vielleicht ernten Sie Proteste, jedoch vorrangig wegen der «gut bezahlten, unbefristeten Arbeitsplätze» in Brandenburg. Ihren Tweet hat die Berliner Senatorin Cansel Kiziltepe inzwischen offenbar dennoch gelöscht.
Dass es um die Meinungs- und Pressefreiheit in der Bundesrepublik nicht mehr allzu gut bestellt ist, befürchtet man inzwischen auch schon im Ausland. Der Fall des Journalisten David Bendels, der kürzlich wegen eines Faeser-Memes zu sieben Monaten Haft auf Bewährung verurteilt wurde, führte in diversen Medien zu Empörung. Die Welt versteckte ihre Kritik mit dem Titel «Ein Urteil wie aus einer Diktatur» hinter einer Bezahlschranke.
Unschöne, heutzutage vielleicht strafbare Kommentare würden mir auch zu einigen anderen Themen und Akteuren einfallen. Ein Kandidat wäre der deutsche Bundesgesundheitsminister (ja, er ist es tatsächlich immer noch). Während sich in den USA auf dem Gebiet etwas bewegt und zum Beispiel Robert F. Kennedy Jr. will, dass die Gesundheitsbehörde (CDC) keine Covid-Impfungen für Kinder mehr empfiehlt, möchte Karl Lauterbach vor allem das Corona-Lügengebäude vor dem Einsturz bewahren.
«Ich habe nie geglaubt, dass die Impfungen nebenwirkungsfrei sind», sagte Lauterbach jüngst der ZDF-Journalistin Sarah Tacke. Das steht in krassem Widerspruch zu seiner früher verbreiteten Behauptung, die Gen-Injektionen hätten keine Nebenwirkungen. Damit entlarvt er sich selbst als Lügner. Die Bezeichnung ist absolut berechtigt, dieser Mann dürfte keinerlei politische Verantwortung tragen und das Verhalten verlangt nach einer rechtlichen Überprüfung. Leider ist ja die Justiz anderweitig beschäftigt und hat außerdem selbst keine weiße Weste.
Obendrein kämpfte der Herr Minister für eine allgemeine Impfpflicht. Er beschwor dabei das Schließen einer «Impflücke», wie es die Weltgesundheitsorganisation – die «wegen Trump» in finanziellen Schwierigkeiten steckt – bis heute tut. Die WHO lässt aktuell ihre «Europäische Impfwoche» propagieren, bei der interessanterweise von Covid nicht mehr groß die Rede ist.
Einen «Klima-Leugner» würden manche wohl Nir Shaviv nennen, das ist ja nicht strafbar. Der Astrophysiker weist nämlich die Behauptung von einer Klimakrise zurück. Gemäß seiner Forschung ist mindestens die Hälfte der Erderwärmung nicht auf menschliche Emissionen, sondern auf Veränderungen im Sonnenverhalten zurückzuführen.
Das passt vielleicht auch den «Klima-Hysterikern» der britischen Regierung ins Konzept, die gerade Experimente zur Verdunkelung der Sonne angekündigt haben. Produzenten von Kunstfleisch oder Betreiber von Insektenfarmen würden dagegen vermutlich die Geschichte vom fatalen CO2 bevorzugen. Ihnen würde es besser passen, wenn der verantwortungsvolle Erdenbürger sein Verhalten gründlich ändern müsste.
In unserer völlig verkehrten Welt, in der praktisch jede Verlautbarung außerhalb der abgesegneten Narrative potenziell strafbar sein kann, gehört fast schon Mut dazu, Dinge offen anzusprechen. Im «besten Deutschland aller Zeiten» glaubten letztes Jahr nur noch 40 Prozent der Menschen, ihre Meinung frei äußern zu können. Das ist ein Armutszeugnis, und es sieht nicht gerade nach Besserung aus. Umso wichtiger ist es, dagegen anzugehen.
[Titelbild: Pixabay]
--- Quellen: ---
[1] Zur Orientierung wenigstens ein paar Hinweise zur NS-Vergangenheit deutscher Automobilhersteller:
- Volkswagen
- Porsche
- Daimler-Benz
- BMW
- Audi
- Opel
- Heute: «Auto-Werke für die Rüstung? Rheinmetall prüft Übernahmen»
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 9063ef6b:fd1e9a09
2025-05-07 07:16:54
@ 9063ef6b:fd1e9a09
2025-05-07 07:16:54🛠️ MkDocs on macOS
For my local documentation, I was looking for an open-source tool to create and manage my content. With MkDocs, I found a mature, widely used, and actively maintained solution.
I think this tool is worth writing an article about. I’m still new to it and don’t have much experience yet. What tools do you use to create your documentation locally?
📚 What is MkDocs?
MkDocs is an open source tool for building static websites from Markdown files, designed specifically for technical documentation.

✅ Key Features
| Feature | Description | |---------------------------|----------------------------------------------------------------------------| | 📄 Markdown-based | Write content in
.mdfiles (e.g., with Zettlr, VS Code, Obsidian) | | 🌐 Static site output | MkDocs renders a full HTML site with navigation, search, and styling | | 🎨 Themes available | Most popular: Material for MkDocs | | 🔄 Live preview | Usemkdocs serveto view the docs locally in your browser | | 🔧 Simple configuration | Controlled via a singlemkdocs.ymlfile | | 🔐 No cloud required | Fully local, ideal for privacy and offline work |
📦 Is MkDocs open source?
Yes. MkDocs is fully open source and licensed under the MIT License – free to use, modify, and redistribute.
- 🔗 GitHub: github.com/mkdocs/mkdocs
- 🔗 PyPI: pypi.org/project/mkdocs
🔧 What can you build with MkDocs?
Examples include:
- Internal IT or team documentation
- Project or API documentation (e.g., GitHub projects)
- Manuals, Wikis, or checklists
- Offline technical knowledge bases
✅ Requirements
- macOS (e.g., Ventura, Sonoma)
- Terminal basics
- Python installed
🔧 Step 1: Install MkDocs
Install MkDocs locally for your user:
bash pip3 install --user mkdocs(Optional) Add the Material theme:
bash pip3 install --user mkdocs-materialThis gives your documentation a modern, responsive design.
🧭 Step 2: Make the
mkdocscommand availableBy default, pip installs MkDocs in a directory not included in your PATH. To fix that:
a) Check install location:
bash python3 -m site --user-baseExample output:
/Users/yourname/Library/Python/3.11The relevant binary path is:
/Users/yourname/Library/Python/3.11/binb) Add to PATH permanently (zsh):
bash echo 'export PATH=$PATH:/Users/yourname/Library/Python/3.11/bin' >> ~/.zshrc source ~/.zshrcReplace Python version if needed (
3.11).
🚀 Step 3: Start a new MkDocs project
bash mkdocs new my-docs cd my-docs mkdocs serveNow open: http://127.0.0.1:8000
🎨 Step 4: Enable the Material Theme
Edit
mkdocs.yml:yaml theme: name: materialThen restart:
bash mkdocs serve
🧩 Alternative: Run via Python module
If you see this error:
zsh: command not found: mkdocs… you can always run MkDocs via:
bash python3 -m mkdocs serve
📚 MkDocs Awesome Pages Plugin
The
awesome-pagesplugin for MkDocs automatically builds navigation from your folder structure – no need to manually definenav:inmkdocs.yml.
✅ Open Source
- License: MIT
- Repo: github.com/lukasgeiter/mkdocs-awesome-pages-plugin
🛠️ Installation
Install with pip:
bash pip3 install mkdocs-awesome-pages-plugin
⚙️ Configure
mkdocs.ymlAdd the plugin:
yaml plugins: - search - awesome-pages⚠️ Remove the
nav:section if you use this plugin – it will otherwise be ignored.
📁 Folder structure &
.pagesfilesNavigation is based on the folder structure under
docs/.Example structure:
docs/ ├── index.md ├── installation/ │ ├── prerequisites.md │ └── setup.md ├── usage/ │ ├── start.md │ └── features.md→ The plugin auto-generates a menu from this.
🔍 Example
mkdocs.ymlwith plugin```yaml site_name: My Tech Docs theme: name: material
plugins: - search - awesome-pages
markdown_extensions: - admonition - toc: permalink: true ```
🔗 Further Resources
- 📘 GitHub: mkdocs-awesome-pages-plugin
- 📘 PyPI: pypi.org/project/mkdocs-awesome-pages-plugin
-
 @ 90c656ff:9383fd4e
2025-05-06 13:01:45
@ 90c656ff:9383fd4e
2025-05-06 13:01:45Bitcoin has revolutionized the way people conduct financial transactions worldwide. As a decentralized digital currency, it offers new opportunities for e-commerce payments and international money transfers. Its speed, security, and low costs make it an efficient alternative to traditional methods by eliminating intermediaries and facilitating global transactions.
Bitcoin in e-commerce
E-commerce has grown exponentially, and Bitcoin has emerged as an innovative solution for online payments. Large retailers and small businesses are starting to accept Bitcoin as a form of payment, offering benefits to both merchants and consumers.
- Advantages of Bitcoin for e-commerce:
01 - Low transaction fees: Unlike credit cards and payment platforms that charge high fees, Bitcoin transactions generally have lower costs. This benefits merchants, who can reduce expenses and offer more competitive prices to customers. 02 - Elimination of chargebacks: In traditional systems, chargebacks (forced refunds by banks or card operators) are a concern for merchants. Since Bitcoin transactions are irreversible, merchants avoid fraud and disputes. 03 - Global access: Anyone with internet access can pay with Bitcoin, regardless of their location. This allows businesses to expand their market internationally without relying on banks or local payment systems. 04 - Privacy and security: Bitcoin transactions protect user identity, offering greater privacy compared to credit card payments or bank transfers. Additionally, since there’s no need to share personal data, the risk of information theft is reduced.
- Challenges of using Bitcoin in e-commerce:
01 - Volatility: Bitcoin’s price can fluctuate rapidly, making it difficult to set fixed prices for products and services. However, some merchants use payment processors that instantly convert Bitcoin into fiat currency, minimizing this risk. 02 - Limited adoption: Despite its growth, Bitcoin acceptance is not yet universal. Many stores and popular platforms have not adopted it, which can make daily purchases difficult. 03 - Confirmation time: Although Bitcoin is faster than traditional bank transfers, confirmation times may vary depending on the network fee paid. Some solutions, such as the Lightning Network, are being developed to enable instant payments.
Bitcoin in money remittances
Sending money abroad has long been a bureaucratic, costly, and time-consuming process. Traditional services like banks and money transfer companies charge high fees and can take days to complete a transaction. Bitcoin, on the other hand, offers an efficient alternative for global remittances, allowing anyone to send and receive money quickly and affordably.
- Benefits of Bitcoin for remittances:
01 - Reduced costs: While banks and companies like Western Union charge high fees for international transfers, Bitcoin allows money to be sent with minimal costs, regardless of the amount or destination. 02 - Transaction speed: International bank transfers can take several days to complete, especially in countries with limited financial infrastructure. With Bitcoin, money can be sent anywhere in the world within minutes or hours. 03 - Global accessibility: In regions where the banking system is restricted or inefficient, Bitcoin enables people to receive money without depending on banks. This is particularly useful in developing countries where international remittances are an essential source of income. 04 - Independence from intermediaries: Bitcoin operates in a decentralized manner, with no need for banks or transfer companies. This means people can send money directly to friends and family without intermediaries.
- Challenges of Bitcoin remittances:
01 - Conversion to local currency: Although Bitcoin can be received instantly, many people still need to convert it into local currency for everyday use. This may involve additional costs and depend on the availability of exchange services. 02 - Adoption and knowledge: Not everyone understands how Bitcoin works, which can hinder its widespread adoption for remittances. However, growing financial education on the subject can help overcome this barrier. 03 - Regulations and restrictions: Some governments impose restrictions on Bitcoin usage, making remittances more complicated. The evolution of regulations may affect ease of use in certain countries.
In summary, Bitcoin is transforming e-commerce and money remittances around the world. Its ability to eliminate intermediaries, reduce costs, and provide fast and secure payments makes it a viable alternative to traditional financial systems.
In e-commerce, it benefits both merchants and consumers by lowering fees and enhancing privacy. In the remittance sector, it facilitates money transfers to any part of the world, especially for those living in countries with inefficient banking systems.
Despite the challenges, Bitcoin adoption continues to grow, driven by innovative solutions and recognition of its potential as a global payment method. As more businesses and individuals embrace this technology, its presence in e-commerce and international remittances will become increasingly relevant.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ 38d2a406:ad9e5329
2025-05-07 02:13:46
@ 38d2a406:ad9e5329
2025-05-07 02:13:46{"contract_id":"f5523a8f242339bdd8585e5491a82c2d9a72ff51f7fadc3f7c6f766afe9c0f19","title":"T2- Freelance Development Agreement","content":"# Freelance Development Agreement\n\n## Parties\n\nThis Freelance Development Agreement (the \"Agreement\") is entered into as of [DATE] by and between:\n\nClient: [CLIENT NAME], with an address at [CLIENT ADDRESS] (\"Client\")\n\nDeveloper: [DEVELOPER NAME], with an address at [DEVELOPER ADDRESS] (\"Developer\")\n\n## Services\n\nDeveloper agrees to provide the following services to Client (the \"Services\"):\n\n1. Design and develop a web application according to the specifications outlined in Attachment A.\n2. Provide regular progress updates on a weekly basis.\n3. Deliver the completed project by the deadline specified in the Timeline section.","version":1,"created_at":1746583812,"signers_required":2,"signatures":[{"pubkey":"306555fee4433582b32f6d46f11b644da33896595016893d7da18c75fd7fdf12","sig":"8ad3a9e2a4ef70515853e051882ab11ebc7d56f15be46deb1520d6292711bc4eeb29c723c46a251c98134d06b8950931d19f61f6f8836e4932f0d6682fe8159e","timestamp":1746583928},{"pubkey":"38d2a406f9ae6eebbeee9d35276c45538ed80083c859b28601279187ad9e5329","sig":"ef4802ea6966318774cb8554ed547692691d143cef48bc1049ef43546b77b3720908ec4e77e151117bafb676b96653cb5fcc70658116e96759d3a2a52ffd94da","timestamp":1746584026}]}
-
 @ 8d34bd24:414be32b
2025-05-07 21:47:57
@ 8d34bd24:414be32b
2025-05-07 21:47:57I’ve been really deeply studying end times prophecy today. Trying to see how all of the prophecies from the initial proto-Gospel in Genesis 3 through the last chapter in Revelation is hard to arrange in my head. That being said, after reading the Bible daily for about 40 years and reading through it each year for about 30 years, I am really starting to see so many links between passages through out the Bible. It has made my Bible study enthralling. I wish I had time to spend hours and hours every day studying and writing about what I have learned.
I thought it might be handy to share some hints on how I study the Bible. Hopefully this can help some people, although I do tend to think my subscribers tend to be those who love Bible study and are already in the word. People who don’t love the Bible are unlikely to read my long, scripture laden posts. Still, hopefully this will be useful.
Starting the Habit of Bible Reading
The first and foremost thing we all need is to start the habit of daily Bible reading. You can’t worship a God you don’t know about and you can’t obey a God whose commands you don’t know. Every Christian needs to read the whole Bible. This needs to be a priority.
I used to recommend people just start at the beginning, Genesis, and read straight through to Revelation, but I’ve lately changed my mind. So many people will start in Genesis, enjoy Genesis and Exodus, which are basically just stories about creation, judgment in the global flood, and God’s chosen people. They then get to Leviticus, Numbers, and Deuteronomy (the details of the law including the intricate ceremonial law) and they lose momentum in the tedium. I do think every Christian eventually needs to read and know these books, but I think it is OK to skip some or all of them the first time through. They will mean more once you have read the whole Bible. If you are only going to read one, I’d probably read Deuteronomy.
I also know that it can be helpful for some people to mix up their reading. I used to have book marks with daily readings, so I read some Old Testament, some Psalms/Proverbs, some New Testament. There was one other category, but I can’t remember what it was. This way, you get a little of different types of passages. My bookmarks burnt up when my house burnt down and when I went searching online for something similar, I found a few similar reading plans, but not the one I used and really liked. Here are a couple that looked good, but I haven’t used myself. here. here. here. These plans look good, but don’t have the convenient bookmarks. here. here. For those who like reading online or on your phone (which isn’t me), I found this one. It looked nice I’ve just started using it despite the fact I prefer a Bible I can hold, turn the pages of, and write in. It has a chronological Old Testament Passage and a New Testament reading that relates in some way to the Old Testament Passage. It also links to some maps that let you see where the places mentioned in the passages are located and questions to get you to think about what you read. The one downside is it only lets you attach notes if you create a group. I do really like the idea that you can setup a group to read through the Bible and share your comments and thoughts, but I haven’t tried the feature.
Another thing I’ve found very helpful is a chronological Bible. It is handy having things in the order they happened and the different passages that cover an event (such as from each gospel or 1/2 Samuel vs 1/2 Chronicles or Leviticus vs Deuteronomy, etc.) right by each other. It is handy to see what actually comes before what and the way different writers describe the same event, since different authors include different details. I think reading a chronological Bible has helped me see more links between passages and get a better understanding of the Bible as a whole. I am getting close to finishing my second reading through. I don’t know if one chronological Bible is significantly better than another, but this is the one I am reading right now.
Another tactic I have used, when I started getting bogged down reading through the Bible again and again was to study one book of the Bible in depth. It worked best reading one of the shorter books. I’d read through the book repeatedly for a month, usually in 1-3 days. I’d follow the links in my study Bible to related passages or study where some of the words were used in other parts of the Bible. I’d get so I really knew the book well.
One thing that has helped me with my Bible study is writing in my Bible. The first time I wrote, it felt almost sacrilegious, but it helps me to organize my thoughts. I’ll write what I get out of it, how it relates to another passage, etc. I’ll underline or circle key words or sentences. These are then useful when I read through again and may see something different, but it reminds me of my growth and learning. I’ve actually thought I really need to get a new wide margin Bible to have more room for my notes. I can write really small and have an ultrafine point pen, so I can write even smaller than the print. The problem is my eyes aren’t so good and I now have trouble reading my tiny print. I can’t read my own writing without my reading glasses.
Bible reading starts getting really exciting when you get to know the Bible well enough that you start seeing the links between different passages and different books. Suddenly it opens up a whole new level of understanding. It is like an exciting scavenger hunt finding how all of the ideas in the Bible relate to each other and clarify each other in one whole.
Historically I’ve hated writing. The thought of writing a journal or something sounded like torture, but I have truly found organizing my thoughts in an essay, really helps my understanding of the Scriptures in ways that reading and thinking about it never did. Whether anyone reads my writings or not, I’ll continue writing because it is a blessing to me. I have grown immensely in my understanding of the Bible by writing out a reasoned argument for what I believe the Bible is saying. I’ve also done in depth study and realized that I was not completely right in my understanding and had to adjust my understanding of Scripture.
but sanctify Christ as Lord in your hearts, always being ready to make a defense to everyone who asks you to give an account for the hope that is in you, yet with gentleness and reverence (1 Peter 3:15)
As Christians, we are supposed to be ready to make a defense. Reading, studying, and knowing the Bible is the only true way to be ready. I made a necklace with the first letter in each word in this verse to help me memorize it.

Memorizing God’s word is also well worth the effort. I’ll admit, that I would be terrible for following my own advice in this, except I have a special needs son, who is in Awana, and needs help memorizing 1-5 verses a week. The only way either of us can pull it off is I make a song for each 1-3 verse passage that he has to memorize. We then sing them together until we know them. I debated on whether to share my songs. They are not well done. The version uploaded is my first rough attempt at the song and we usually fine tune them over the week, but I don’t get around to rerecording them. I also have at best an OK voice. Still, I decided to share in case these songs can help someone else with their Bible memorization. Hopefully I am not embarrassing myself too much.
Another thing that has helped me is finding Open Bible’s geocoding site. When reading Bible passages, there are frequent references to places that are unfamiliar, either because they are far away or because the ancient names, rather than modern names, are used. This site allows you to see on a map (satellite & modern country formats) where places are located and how they relate to each other. I’ve especially found this useful with end times prophecy because the Bible describes places with their ancient, not modern names.
In addition to my direct Bible study, I also daily listen to sermons, Christian podcasts, read Christian substack posts, and read Christian commentaries. All help my understanding of the Bible. FYI, the sermons, podcasts, blogs, and commentaries are a risk if you don’t know the Bible and aren’t being like the Bereans who searched “… the Scriptures daily to see whether these things were so.” (Acts 17:11) There are so many false or erroneous teachers, that you have to be very careful listening to people and never put the opinions of men above the word of God. Of course, it is possible to learn a bunch from Godly teachers. Sadly, even the best Bible teachers seem to have at least one area of error. For example, I love listening to R.C. Sproul’s “Renewing Your Mind” podcast, but his teaching on the first 11 chapters of Genesis are a bit “squishy” (not outright wrong, but not holding firm enough to the Bible) and I’d say his end times teaching is flat out wrong. Everything I’ve heard him teach between Genesis 12 and Jude is amazing and very true to the Bible. This is where he spends almost all of his time teaching, so I can highly recommend his podcast. Without a firm foundation in the Bible, it is not possible to recognize false teaching, especially when taught by someone who is very good in most respects.
I hope this is useful to people to help them get into the habit of regular Bible reading and seeing how exciting Bible study can be.
May God give you a hunger for and understanding of His word. May you fill your heart and mind with the word of God so it overflows and is seen by all around you.
Trust Jesus.
-
 @ c631e267:c2b78d3e
2025-04-20 19:54:32
@ c631e267:c2b78d3e
2025-04-20 19:54:32Es ist völlig unbestritten, dass der Angriff der russischen Armee auf die Ukraine im Februar 2022 strikt zu verurteilen ist. Ebenso unbestritten ist Russland unter Wladimir Putin keine brillante Demokratie. Aus diesen Tatsachen lässt sich jedoch nicht das finstere Bild des russischen Präsidenten – und erst recht nicht des Landes – begründen, das uns durchweg vorgesetzt wird und den Kern des aktuellen europäischen Bedrohungs-Szenarios darstellt. Da müssen wir schon etwas genauer hinschauen.
Der vorliegende Artikel versucht derweil nicht, den Einsatz von Gewalt oder die Verletzung von Menschenrechten zu rechtfertigen oder zu entschuldigen – ganz im Gegenteil. Dass jedoch der Verdacht des «Putinverstehers» sofort latent im Raume steht, verdeutlicht, was beim Thema «Russland» passiert: Meinungsmache und Manipulation.
Angesichts der mentalen Mobilmachung seitens Politik und Medien sowie des Bestrebens, einen bevorstehenden Krieg mit Russland geradezu herbeizureden, ist es notwendig, dieser fatalen Entwicklung entgegenzutreten. Wenn wir uns nur ein wenig von der herrschenden Schwarz-Weiß-Malerei freimachen, tauchen automatisch Fragen auf, die Risse im offiziellen Narrativ enthüllen. Grund genug, nachzuhaken.
Wer sich schon länger auch abseits der Staats- und sogenannten Leitmedien informiert, der wird in diesem Artikel vermutlich nicht viel Neues erfahren. Andere könnten hier ein paar unbekannte oder vergessene Aspekte entdecken. Möglicherweise klärt sich in diesem Kontext die Wahrnehmung der aktuellen (unserer eigenen!) Situation ein wenig.
Manipulation erkennen
Corona-«Pandemie», menschengemachter Klimawandel oder auch Ukraine-Krieg: Jede Menge Krisen, und für alle gibt es ein offizielles Narrativ, dessen Hinterfragung unerwünscht ist. Nun ist aber ein Narrativ einfach eine Erzählung, eine Geschichte (Latein: «narratio») und kein Tatsachenbericht. Und so wie ein Märchen soll auch das Narrativ eine Botschaft vermitteln.
Über die Methoden der Manipulation ist viel geschrieben worden, sowohl in Bezug auf das Individuum als auch auf die Massen. Sehr wertvolle Tipps dazu, wie man Manipulationen durchschauen kann, gibt ein Büchlein [1] von Albrecht Müller, dem Herausgeber der NachDenkSeiten.
Die Sprache selber eignet sich perfekt für die Manipulation. Beispielsweise kann die Wortwahl Bewertungen mitschwingen lassen, regelmäßiges Wiederholen (gerne auch von verschiedenen Seiten) lässt Dinge irgendwann «wahr» erscheinen, Übertreibungen fallen auf und hinterlassen wenigstens eine Spur im Gedächtnis, genauso wie Andeutungen. Belege spielen dabei keine Rolle.
Es gibt auffällig viele Sprachregelungen, die offenbar irgendwo getroffen und irgendwie koordiniert werden. Oder alle Redenschreiber und alle Medien kopieren sich neuerdings permanent gegenseitig. Welchen Zweck hat es wohl, wenn der Krieg in der Ukraine durchgängig und quasi wörtlich als «russischer Angriffskrieg auf die Ukraine» bezeichnet wird? Obwohl das in der Sache richtig ist, deutet die Art der Verwendung auf gezielte Beeinflussung hin und soll vor allem das Feindbild zementieren.
Sprachregelungen dienen oft der Absicherung einer einseitigen Darstellung. Das Gleiche gilt für das Verkürzen von Informationen bis hin zum hartnäckigen Verschweigen ganzer Themenbereiche. Auch hierfür gibt es rund um den Ukraine-Konflikt viele gute Beispiele.
Das gewünschte Ergebnis solcher Methoden ist eine Schwarz-Weiß-Malerei, bei der einer eindeutig als «der Böse» markiert ist und die anderen automatisch «die Guten» sind. Das ist praktisch und demonstriert gleichzeitig ein weiteres Manipulationswerkzeug: die Verwendung von Doppelstandards. Wenn man es schafft, bei wichtigen Themen regelmäßig mit zweierlei Maß zu messen, ohne dass das Publikum protestiert, dann hat man freie Bahn.
Experten zu bemühen, um bestimmte Sachverhalte zu erläutern, ist sicher sinnvoll, kann aber ebenso missbraucht werden, schon allein durch die Auswahl der jeweiligen Spezialisten. Seit «Corona» werden viele erfahrene und ehemals hoch angesehene Fachleute wegen der «falschen Meinung» diffamiert und gecancelt. [2] Das ist nicht nur ein brutaler Umgang mit Menschen, sondern auch eine extreme Form, die öffentliche Meinung zu steuern.
Wann immer wir also erkennen (weil wir aufmerksam waren), dass wir bei einem bestimmten Thema manipuliert werden, dann sind zwei logische und notwendige Fragen: Warum? Und was ist denn richtig? In unserem Russland-Kontext haben die Antworten darauf viel mit Geopolitik und Geschichte zu tun.
Ist Russland aggressiv und expansiv?
Angeblich plant Russland, europäische NATO-Staaten anzugreifen, nach dem Motto: «Zuerst die Ukraine, dann den Rest». In Deutschland weiß man dafür sogar das Datum: «Wir müssen bis 2029 kriegstüchtig sein», versichert Verteidigungsminister Pistorius.
Historisch gesehen ist es allerdings eher umgekehrt: Russland, bzw. die Sowjetunion, ist bereits dreimal von Westeuropa aus militärisch angegriffen worden. Die Feldzüge Napoleons, des deutschen Kaiserreichs und Nazi-Deutschlands haben Millionen Menschen das Leben gekostet. Bei dem ausdrücklichen Vernichtungskrieg ab 1941 kam es außerdem zu Brutalitäten wie der zweieinhalbjährigen Belagerung Leningrads (heute St. Petersburg) durch Hitlers Wehrmacht. Deren Ziel, die Bevölkerung auszuhungern, wurde erreicht: über eine Million tote Zivilisten.
Trotz dieser Erfahrungen stimmte Michail Gorbatschow 1990 der deutschen Wiedervereinigung zu und die Sowjetunion zog ihre Truppen aus Osteuropa zurück (vgl. Abb. 1). Der Warschauer Pakt wurde aufgelöst, der Kalte Krieg formell beendet. Die Sowjets erhielten damals von führenden westlichen Politikern die Zusicherung, dass sich die NATO «keinen Zentimeter ostwärts» ausdehnen würde, das ist dokumentiert. [3]

Expandiert ist die NATO trotzdem, und zwar bis an Russlands Grenzen (vgl. Abb. 2). Laut dem Politikberater Jeffrey Sachs handelt es sich dabei um ein langfristiges US-Projekt, das von Anfang an die Ukraine und Georgien mit einschloss. Offiziell wurde der Beitritt beiden Staaten 2008 angeboten. In jedem Fall könnte die massive Ost-Erweiterung seit 1999 aus russischer Sicht nicht nur als Vertrauensbruch, sondern durchaus auch als aggressiv betrachtet werden.

Russland hat den europäischen Staaten mehrfach die Hand ausgestreckt [4] für ein friedliches Zusammenleben und den «Aufbau des europäischen Hauses». Präsident Putin sei «in seiner ersten Amtszeit eine Chance für Europa» gewesen, urteilt die Journalistin und langjährige Russland-Korrespondentin der ARD, Gabriele Krone-Schmalz. Er habe damals viele positive Signale Richtung Westen gesendet.
Die Europäer jedoch waren scheinbar an einer Partnerschaft mit dem kontinentalen Nachbarn weniger interessiert als an der mit dem transatlantischen Hegemon. Sie verkennen bis heute, dass eine gedeihliche Zusammenarbeit in Eurasien eine Gefahr für die USA und deren bekundetes Bestreben ist, die «einzige Weltmacht» zu sein – «Full Spectrum Dominance» [5] nannte das Pentagon das. Statt einem neuen Kalten Krieg entgegenzuarbeiten, ließen sich europäische Staaten selber in völkerrechtswidrige «US-dominierte Angriffskriege» [6] verwickeln, wie in Serbien, Afghanistan, dem Irak, Libyen oder Syrien. Diese werden aber selten so benannt.

Speziell den Deutschen stünde außer einer Portion Realismus auch etwas mehr Dankbarkeit gut zu Gesicht. Das Geschichtsbewusstsein der Mehrheit scheint doch recht selektiv und das Selbstbewusstsein einiger etwas desorientiert zu sein. Bekanntermaßen waren es die Soldaten der sowjetischen Roten Armee, die unter hohen Opfern 1945 Deutschland «vom Faschismus befreit» haben. Bei den Gedenkfeiern zu 80 Jahren Kriegsende will jedoch das Auswärtige Amt – noch unter der Diplomatie-Expertin Baerbock, die sich schon länger offiziell im Krieg mit Russland wähnt, – nun keine Russen sehen: Sie sollen notfalls rausgeschmissen werden.
«Die Grundsatzfrage lautet: Geht es Russland um einen angemessenen Platz in einer globalen Sicherheitsarchitektur, oder ist Moskau schon seit langem auf einem imperialistischen Trip, der befürchten lassen muss, dass die Russen in fünf Jahren in Berlin stehen?»
So bringt Gabriele Krone-Schmalz [7] die eigentliche Frage auf den Punkt, die zur Einschätzung der Situation letztlich auch jeder für sich beantworten muss.
Was ist los in der Ukraine?
In der internationalen Politik geht es nie um Demokratie oder Menschenrechte, sondern immer um Interessen von Staaten. Diese These stammt von Egon Bahr, einem der Architekten der deutschen Ostpolitik des «Wandels durch Annäherung» aus den 1960er und 70er Jahren. Sie trifft auch auf den Ukraine-Konflikt zu, den handfeste geostrategische und wirtschaftliche Interessen beherrschen, obwohl dort angeblich «unsere Demokratie» verteidigt wird.
Es ist ein wesentliches Element des Ukraine-Narrativs und Teil der Manipulation, die Vorgeschichte des Krieges wegzulassen – mindestens die vor der russischen «Annexion» der Halbinsel Krim im März 2014, aber oft sogar komplett diejenige vor der Invasion Ende Februar 2022. Das Thema ist komplex, aber einige Aspekte, die für eine Beurteilung nicht unwichtig sind, will ich wenigstens kurz skizzieren. [8]
Das Gebiet der heutigen Ukraine und Russlands – die übrigens in der «Kiewer Rus» gemeinsame Wurzeln haben – hat der britische Geostratege Halford Mackinder bereits 1904 als eurasisches «Heartland» bezeichnet, dessen Kontrolle er eine große Bedeutung für die imperiale Strategie Großbritanniens zumaß. Für den ehemaligen Sicherheits- und außenpolitischen Berater mehrerer US-amerikanischer Präsidenten und Mitgründer der Trilateralen Kommission, Zbigniew Brzezinski, war die Ukraine nach der Auflösung der Sowjetunion ein wichtiger Spielstein auf dem «eurasischen Schachbrett», wegen seiner Nähe zu Russland, seiner Bodenschätze und seines Zugangs zum Schwarzen Meer.
Die Ukraine ist seit langem ein gespaltenes Land. Historisch zerrissen als Spielball externer Interessen und geprägt von ethnischen, kulturellen, religiösen und geografischen Unterschieden existiert bis heute, grob gesagt, eine Ost-West-Spaltung, welche die Suche nach einer nationalen Identität stark erschwert.
Insbesondere im Zuge der beiden Weltkriege sowie der Russischen Revolution entstanden tiefe Risse in der Bevölkerung. Ukrainer kämpften gegen Ukrainer, zum Beispiel die einen auf der Seite von Hitlers faschistischer Nazi-Armee und die anderen auf der von Stalins kommunistischer Roter Armee. Die Verbrechen auf beiden Seiten sind nicht vergessen. Dass nach der Unabhängigkeit 1991 versucht wurde, Figuren wie den radikalen Nationalisten Symon Petljura oder den Faschisten und Nazi-Kollaborateur Stepan Bandera als «Nationalhelden» zu installieren, verbessert die Sache nicht.
Während die USA und EU-Staaten zunehmend «ausländische Einmischung» (speziell russische) in «ihre Demokratien» wittern, betreiben sie genau dies seit Jahrzehnten in vielen Ländern der Welt. Die seit den 2000er Jahren bekannten «Farbrevolutionen» in Osteuropa werden oft als Methode des Regierungsumsturzes durch von außen gesteuerte «demokratische» Volksaufstände beschrieben. Diese Strategie geht auf Analysen zum «Schwarmverhalten» [9] seit den 1960er Jahren zurück (Studentenproteste), wo es um die potenzielle Wirksamkeit einer «rebellischen Hysterie» von Jugendlichen bei postmodernen Staatsstreichen geht. Heute nennt sich dieses gezielte Kanalisieren der Massen zur Beseitigung unkooperativer Regierungen «Soft-Power».
In der Ukraine gab es mit der «Orangen Revolution» 2004 und dem «Euromaidan» 2014 gleich zwei solcher «Aufstände». Der erste erzwang wegen angeblicher Unregelmäßigkeiten eine Wiederholung der Wahlen, was mit Wiktor Juschtschenko als neuem Präsidenten endete. Dieser war ehemaliger Direktor der Nationalbank und Befürworter einer Annäherung an EU und NATO. Seine Frau, die First Lady, ist US-amerikanische «Philanthropin» und war Beamtin im Weißen Haus in der Reagan- und der Bush-Administration.
Im Gegensatz zu diesem ersten Event endete der sogenannte Euromaidan unfriedlich und blutig. Die mehrwöchigen Proteste gegen Präsident Wiktor Janukowitsch, in Teilen wegen des nicht unterzeichneten Assoziierungsabkommens mit der EU, wurden zunehmend gewalttätiger und von Nationalisten und Faschisten des «Rechten Sektors» dominiert. Sie mündeten Ende Februar 2014 auf dem Kiewer Unabhängigkeitsplatz (Maidan) in einem Massaker durch Scharfschützen. Dass deren Herkunft und die genauen Umstände nicht geklärt wurden, störte die Medien nur wenig. [10]
Janukowitsch musste fliehen, er trat nicht zurück. Vielmehr handelte es sich um einen gewaltsamen, allem Anschein nach vom Westen inszenierten Putsch. Laut Jeffrey Sachs war das kein Geheimnis, außer vielleicht für die Bürger. Die USA unterstützten die Post-Maidan-Regierung nicht nur, sie beeinflussten auch ihre Bildung. Das geht unter anderem aus dem berühmten «Fuck the EU»-Telefonat der US-Chefdiplomatin für die Ukraine, Victoria Nuland, mit Botschafter Geoffrey Pyatt hervor.
Dieser Bruch der demokratischen Verfassung war letztlich der Auslöser für die anschließenden Krisen auf der Krim und im Donbass (Ostukraine). Angesichts der ukrainischen Geschichte mussten die nationalistischen Tendenzen und die Beteiligung der rechten Gruppen an dem Umsturz bei der russigsprachigen Bevölkerung im Osten ungute Gefühle auslösen. Es gab Kritik an der Übergangsregierung, Befürworter einer Abspaltung und auch für einen Anschluss an Russland.
Ebenso konnte Wladimir Putin in dieser Situation durchaus Bedenken wegen des Status der russischen Militärbasis für seine Schwarzmeerflotte in Sewastopol auf der Krim haben, für die es einen langfristigen Pachtvertrag mit der Ukraine gab. Was im März 2014 auf der Krim stattfand, sei keine Annexion, sondern eine Abspaltung (Sezession) nach einem Referendum gewesen, also keine gewaltsame Aneignung, urteilte der Rechtswissenschaftler Reinhard Merkel in der FAZ sehr detailliert begründet. Übrigens hatte die Krim bereits zu Zeiten der Sowjetunion den Status einer autonomen Republik innerhalb der Ukrainischen SSR.
Anfang April 2014 wurden in der Ostukraine die «Volksrepubliken» Donezk und Lugansk ausgerufen. Die Kiewer Übergangsregierung ging unter der Bezeichnung «Anti-Terror-Operation» (ATO) militärisch gegen diesen, auch von Russland instrumentalisierten Widerstand vor. Zufällig war kurz zuvor CIA-Chef John Brennan in Kiew. Die Maßnahmen gingen unter dem seit Mai neuen ukrainischen Präsidenten, dem Milliardär Petro Poroschenko, weiter. Auch Wolodymyr Selenskyj beendete den Bürgerkrieg nicht, als er 2019 vom Präsidenten-Schauspieler, der Oligarchen entmachtet, zum Präsidenten wurde. Er fuhr fort, die eigene Bevölkerung zu bombardieren.
Mit dem Einmarsch russischer Truppen in die Ostukraine am 24. Februar 2022 begann die zweite Phase des Krieges. Die Wochen und Monate davor waren intensiv. Im November hatte die Ukraine mit den USA ein Abkommen über eine «strategische Partnerschaft» unterzeichnet. Darin sagten die Amerikaner ihre Unterstützung der EU- und NATO-Perspektive der Ukraine sowie quasi für die Rückeroberung der Krim zu. Dagegen ließ Putin der NATO und den USA im Dezember 2021 einen Vertragsentwurf über beiderseitige verbindliche Sicherheitsgarantien zukommen, den die NATO im Januar ablehnte. Im Februar eskalierte laut OSZE die Gewalt im Donbass.
Bereits wenige Wochen nach der Invasion, Ende März 2022, kam es in Istanbul zu Friedensverhandlungen, die fast zu einer Lösung geführt hätten. Dass der Krieg nicht damals bereits beendet wurde, lag daran, dass der Westen dies nicht wollte. Man war der Meinung, Russland durch die Ukraine in diesem Stellvertreterkrieg auf Dauer militärisch schwächen zu können. Angesichts von Hunderttausenden Toten, Verletzten und Traumatisierten, die als Folge seitdem zu beklagen sind, sowie dem Ausmaß der Zerstörung, fehlen einem die Worte.
Hasst der Westen die Russen?
Diese Frage drängt sich auf, wenn man das oft unerträglich feindselige Gebaren beobachtet, das beileibe nicht neu ist und vor Doppelmoral trieft. Russland und speziell die Person Wladimir Putins werden regelrecht dämonisiert, was gleichzeitig scheinbar jede Form von Diplomatie ausschließt.
Russlands militärische Stärke, seine geografische Lage, sein Rohstoffreichtum oder seine unabhängige diplomatische Tradition sind sicher Störfaktoren für das US-amerikanische Bestreben, der Boss in einer unipolaren Welt zu sein. Ein womöglich funktionierender eurasischer Kontinent, insbesondere gute Beziehungen zwischen Russland und Deutschland, war indes schon vor dem Ersten Weltkrieg eine Sorge des britischen Imperiums.
Ein «Vergehen» von Präsident Putin könnte gewesen sein, dass er die neoliberale Schocktherapie à la IWF und den Ausverkauf des Landes (auch an US-Konzerne) beendete, der unter seinem Vorgänger herrschte. Dabei zeigte er sich als Führungspersönlichkeit und als nicht so formbar wie Jelzin. Diese Aspekte allein sind aber heute vermutlich keine ausreichende Erklärung für ein derart gepflegtes Feindbild.
Der Historiker und Philosoph Hauke Ritz erweitert den Fokus der Fragestellung zu: «Warum hasst der Westen die Russen so sehr?», was er zum Beispiel mit dem Medienforscher Michael Meyen und mit der Politikwissenschaftlerin Ulrike Guérot bespricht. Ritz stellt die interessante These [11] auf, dass Russland eine Provokation für den Westen sei, welcher vor allem dessen kulturelles und intellektuelles Potenzial fürchte.
Die Russen sind Europäer aber anders, sagt Ritz. Diese «Fremdheit in der Ähnlichkeit» erzeuge vielleicht tiefe Ablehnungsgefühle. Obwohl Russlands Identität in der europäischen Kultur verwurzelt ist, verbinde es sich immer mit der Opposition in Europa. Als Beispiele nennt er die Kritik an der katholischen Kirche oder die Verbindung mit der Arbeiterbewegung. Christen, aber orthodox; Sozialismus statt Liberalismus. Das mache das Land zum Antagonisten des Westens und zu einer Bedrohung der Machtstrukturen in Europa.
Fazit
Selbstverständlich kann man Geschichte, Ereignisse und Entwicklungen immer auf verschiedene Arten lesen. Dieser Artikel, obwohl viel zu lang, konnte nur einige Aspekte der Ukraine-Tragödie anreißen, die in den offiziellen Darstellungen in der Regel nicht vorkommen. Mindestens dürfte damit jedoch klar geworden sein, dass die Russische Föderation bzw. Wladimir Putin nicht der alleinige Aggressor in diesem Konflikt ist. Das ist ein Stellvertreterkrieg zwischen USA/NATO (gut) und Russland (böse); die Ukraine (edel) wird dabei schlicht verheizt.
Das ist insofern von Bedeutung, als die gesamte europäische Kriegshysterie auf sorgsam kultivierten Freund-Feind-Bildern beruht. Nur so kann Konfrontation und Eskalation betrieben werden, denn damit werden die wahren Hintergründe und Motive verschleiert. Angst und Propaganda sind notwendig, damit die Menschen den Wahnsinn mitmachen. Sie werden belogen, um sie zuerst zu schröpfen und anschließend auf die Schlachtbank zu schicken. Das kann niemand wollen, außer den stets gleichen Profiteuren: die Rüstungs-Lobby und die großen Investoren, die schon immer an Zerstörung und Wiederaufbau verdient haben.
Apropos Investoren: Zu den Top-Verdienern und somit Hauptinteressenten an einer Fortführung des Krieges zählt BlackRock, einer der weltgrößten Vermögensverwalter. Der deutsche Bundeskanzler in spe, Friedrich Merz, der gerne «Taurus»-Marschflugkörper an die Ukraine liefern und die Krim-Brücke zerstören möchte, war von 2016 bis 2020 Aufsichtsratsvorsitzender von BlackRock in Deutschland. Aber das hat natürlich nichts zu sagen, der Mann macht nur seinen Job.
Es ist ein Spiel der Kräfte, es geht um Macht und strategische Kontrolle, um Geheimdienste und die Kontrolle der öffentlichen Meinung, um Bodenschätze, Rohstoffe, Pipelines und Märkte. Das klingt aber nicht sexy, «Demokratie und Menschenrechte» hört sich besser und einfacher an. Dabei wäre eine für alle Seiten förderliche Politik auch nicht so kompliziert; das Handwerkszeug dazu nennt sich Diplomatie. Noch einmal Gabriele Krone-Schmalz:
«Friedliche Politik ist nichts anderes als funktionierender Interessenausgleich. Da geht’s nicht um Moral.»
Die Situation in der Ukraine ist sicher komplex, vor allem wegen der inneren Zerrissenheit. Es dürfte nicht leicht sein, eine friedliche Lösung für das Zusammenleben zu finden, aber die Beteiligten müssen es vor allem wollen. Unter den gegebenen Umständen könnte eine sinnvolle Perspektive mit Neutralität und föderalen Strukturen zu tun haben.
Allen, die sich bis hierher durch die Lektüre gearbeitet (oder auch einfach nur runtergescrollt) haben, wünsche ich frohe Oster-Friedenstage!
[Titelbild: Pixabay; Abb. 1 und 2: nach Ganser/SIPER; Abb. 3: SIPER]
--- Quellen: ---
[1] Albrecht Müller, «Glaube wenig. Hinterfrage alles. Denke selbst.», Westend 2019
[2] Zwei nette Beispiele:
- ARD-faktenfinder (sic), «Viel Aufmerksamkeit für fragwürdige Experten», 03/2023
- Neue Zürcher Zeitung, «Aufstieg und Fall einer Russlandversteherin – die ehemalige ARD-Korrespondentin Gabriele Krone-Schmalz rechtfertigt seit Jahren Putins Politik», 12/2022
[3] George Washington University, «NATO Expansion: What Gorbachev Heard – Declassified documents show security assurances against NATO expansion to Soviet leaders from Baker, Bush, Genscher, Kohl, Gates, Mitterrand, Thatcher, Hurd, Major, and Woerner», 12/2017
[4] Beispielsweise Wladimir Putin bei seiner Rede im Deutschen Bundestag, 25/09/2001
[5] William Engdahl, «Full Spectrum Dominance, Totalitarian Democracy In The New World Order», edition.engdahl 2009
[6] Daniele Ganser, «Illegale Kriege – Wie die NATO-Länder die UNO sabotieren. Eine Chronik von Kuba bis Syrien», Orell Füssli 2016
[7] Gabriele Krone-Schmalz, «Mit Friedensjournalismus gegen ‘Kriegstüchtigkeit’», Vortrag und Diskussion an der Universität Hamburg, veranstaltet von engagierten Studenten, 16/01/2025\ → Hier ist ein ähnlicher Vortrag von ihr (Video), den ich mit spanischer Übersetzung gefunden habe.
[8] Für mehr Hintergrund und Details empfehlen sich z.B. folgende Bücher:
- Mathias Bröckers, Paul Schreyer, «Wir sind immer die Guten», Westend 2019
- Gabriele Krone-Schmalz, «Russland verstehen? Der Kampf um die Ukraine und die Arroganz des Westens», Westend 2023
- Patrik Baab, «Auf beiden Seiten der Front – Meine Reisen in die Ukraine», Fiftyfifty 2023
[9] vgl. Jonathan Mowat, «Washington's New World Order "Democratization" Template», 02/2005 und RAND Corporation, «Swarming and the Future of Conflict», 2000
[10] Bemerkenswert einige Beiträge, von denen man später nichts mehr wissen wollte:
- ARD Monitor, «Todesschüsse in Kiew: Wer ist für das Blutbad vom Maidan verantwortlich», 10/04/2014, Transkript hier
- Telepolis, «Blutbad am Maidan: Wer waren die Todesschützen?», 12/04/2014
- Telepolis, «Scharfschützenmorde in Kiew», 14/12/2014
- Deutschlandfunk, «Gefahr einer Spirale nach unten», Interview mit Günter Verheugen, 18/03/2014
- NDR Panorama, «Putsch in Kiew: Welche Rolle spielen die Faschisten?», 06/03/2014
[11] Hauke Ritz, «Vom Niedergang des Westens zur Neuerfindung Europas», 2024
Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
-
 @ 90c656ff:9383fd4e
2025-05-06 12:18:09
@ 90c656ff:9383fd4e
2025-05-06 12:18:09Digital wallets are important tools for storing and managing Bitcoin. They allow people to keep their private keys, access their funds, and make transactions in a practical and secure way. However, with several types of wallets available and the risks of incorrect use, it is essential to understand their features and follow good security practices.
What is a digital wallet?
A digital wallet is a software or device that stores the private and public keys linked to Bitcoin. Simply put, it doesn’t “store” Bitcoin itself but provides secure access to the network to verify and sign transactions.
Private keys work like a secret password that allows spending Bitcoins, while public keys are like account numbers that can be shared to receive payments. Keeping the private key secure is very important, as whoever has access to it controls the funds.
- Types of Digital Wallets
There are different types of digital wallets, each with specific features that meet various needs, whether for daily use or long-term storage.
- Hot Wallets
Wallets connected to the internet, designed for frequent use. Examples: Mobile apps, desktop wallets, online wallets.
Advantages:
01 - Accessible and easy to use 02 - Ideal for daily and quick transactions
Disadvantages:
01 - More exposed to cyberattacks such as phishing or hacking
- Cold Wallets
Wallets that keep private keys offline, increasing security. Examples: Hardware wallets, paper wallets, dedicated USB devices.
Advantages:
01 - High protection against hackers since they are not online 02 - Ideal for large amounts of Bitcoin or long-term storage
Disadvantages:
01 - Less practical for daily use 02 - Can be physically damaged or lost if not handled carefully
- Hardware Wallets
Physical devices, like Ledger or Trezor, that store private keys offline.
Advantages:
01 - Easy-to-use and secure interface 02 - Resistant to viruses and online attacks
Disadvantages:
01 - Higher initial cost 02 - Require care to avoid physical damage
- Paper Wallets
Involve printing or writing down private and public keys on a piece of paper.
Advantages:
01 - Completely offline and immune to digital attacks 02 - Simple and low-cost
Disadvantages:
01 - Vulnerable to physical damage such as water, fire, or loss 02 - Difficult to recover if lost
- Security in Digital Wallets
Protecting a digital wallet is essential to safeguard your Bitcoins from loss or theft.
Below are important practices to improve security:
- Private Key Protection
01 - Never share your private key with anyone 02 - Keep backup copies of the private key or recovery phrase in safe places
- Use of Recovery Phrases
The seed phrase is a sequence of 12 to 24 words that helps recover funds if the wallet is lost.
01 - Store the seed phrase offline and avoid taking pictures or saving it on internet-connected devices
- Two-Factor Authentication (2FA)
01 - Whenever possible, enable 2FA to protect accounts linked to online wallets or exchanges 02 - This adds an extra layer of security by requiring a second code to log in
- Updates and Maintenance
Keep the wallet software up to date to ensure protection against vulnerabilities
01 - Use only wallets from trustworthy and reputable developers
- Choosing the Right Wallet According to Need
01 - For frequent transactions, choose hot wallets but keep only small amounts 02 - For large amounts, use cold wallets like hardware or paper wallets, which are more secure
Risks and How to Avoid Them
- Hacker Attacks
Risk: Unauthorized access to hot wallets connected to the internet Prevention: Use cold wallets for storing large amounts and avoid clicking on suspicious links
- Loss of Access
Risk: Loss of private keys or the recovery phrase, making funds unrecoverable Prevention: Regularly make backups and store information in secure places
- Social Engineering and Phishing
Risk: Hackers trick people into giving up their private keys or personal information Prevention: Be suspicious of messages or websites that request your private keys. Never share sensitive data
- Physical Failures
Risk: Damage to devices or loss of paper wallets Prevention: Store backups in locations resistant to water, fire, and other threats
In summary, digital wallets are essential for the security and use of Bitcoin. Choosing the right wallet and following good security practices are key steps to protecting your assets.
Hot wallets offer convenience for daily use, while cold wallets provide strong security for long-term storage. Regardless of the type you choose, taking care of your private keys and recovery phrase is fundamental to ensure your Bitcoin remains under your control.
By understanding the types of wallets and implementing appropriate security measures, users can safely and efficiently take advantage of Bitcoin, maximizing the benefits of this digital revolution.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ 557c650b:b04c6817
2025-05-07 19:46:47
@ 557c650b:b04c6817
2025-05-07 19:46:47Um exercício mental
-
 @ a5142938:0ef19da3
2025-05-06 10:36:14
@ a5142938:0ef19da3
2025-05-06 10:36:14What is a natural material? It's a topic of debate, and everyone will prioritize their own criteria. Here’s how materials are classified on this site. The list is regularly updated based on the products added. Feel free to share your thoughts!
✅ Natural Materials
Materials of plant, animal, or mineral origin, without chemical transformation that alters their molecular structure.
🌱 Main Criteria: - Biodegradability - Non-toxicity - Naturally occurring and recquiring minimal transformation
🔍 List of Natural Materials: - Regenerated Cellulose (cupra, lyocell, modal, rayon) - Cork - Cotton - Earth - Glass - Hemp - Natural Latex, rubber - Leather - Linen - Metal - Silk - Wood - Wool - … (Other materials)
⚠️ Although "natural", these materials can have negative impacts depending on their production conditions (pesticide pollution, excessive water consumption, chemical treatments, animal exploitation, etc.). These impacts are mentionned in the description of each material.
Organic versions of these materials — free from chemical treatments, animal mistreatment, etc. — are preferred for listing products on this site, as indicated on each material's page (coming soon).
Conventional versions are only referenced when no more sustainable alternative has yet been found for that product category.
🚫 Non-Natural Materials
Synthetic or heavily modified materials, often derived from petrochemicals.
📌 Main Issues: - Toxicity and microplastic emissions - Dependence on fossil fuels - Poor biodegradability
🔍 List of Non-Natural Materials: - Acrylic - Elastane, spandex, lycra - Polyamides, nylon - Polyester - Silicone - … (Other materials)
⚠️ These materials are not accepted on this site. However, they may be present in certain listed products if:
- they are used in removable accessories (e.g., elastics, buttons—often not listed in the product’s composition by the brand) that can be detached for recycling or composting, and
- no 100% natural alternative has yet been identified for that product category.
In such cases, a warning will be displayed on the product page.
This article is published on origin-nature.com 🌐 Voir cet article en français
-
 @ 306555fe:fd7fdf12
2025-05-07 02:12:08
@ 306555fe:fd7fdf12
2025-05-07 02:12:08{"contract_id":"f5523a8f242339bdd8585e5491a82c2d9a72ff51f7fadc3f7c6f766afe9c0f19","title":"T2- Freelance Development Agreement","content":"# Freelance Development Agreement\n\n## Parties\n\nThis Freelance Development Agreement (the \"Agreement\") is entered into as of [DATE] by and between:\n\nClient: [CLIENT NAME], with an address at [CLIENT ADDRESS] (\"Client\")\n\nDeveloper: [DEVELOPER NAME], with an address at [DEVELOPER ADDRESS] (\"Developer\")\n\n## Services\n\nDeveloper agrees to provide the following services to Client (the \"Services\"):\n\n1. Design and develop a web application according to the specifications outlined in Attachment A.\n2. Provide regular progress updates on a weekly basis.\n3. Deliver the completed project by the deadline specified in the Timeline section.","version":1,"created_at":1746583812,"signers_required":2,"signatures":[{"pubkey":"306555fee4433582b32f6d46f11b644da33896595016893d7da18c75fd7fdf12","sig":"8ad3a9e2a4ef70515853e051882ab11ebc7d56f15be46deb1520d6292711bc4eeb29c723c46a251c98134d06b8950931d19f61f6f8836e4932f0d6682fe8159e","timestamp":1746583928}]}
-
 @ a9e24cc2:597d8933
2025-05-07 01:06:44
@ a9e24cc2:597d8933
2025-05-07 01:06:44𝐌𝐄𝐒𝐒𝐀𝐆𝐄 BlackHat_Nexus 𝐅𝐎𝐑 𝐀𝐍𝐘 𝐊𝐈𝐍𝐃 𝐎𝐅 𝐒𝐄𝐑𝐕𝐈𝐂𝐄 𝐑𝐄𝐂𝐎𝐕𝐄𝐑 𝐘𝐎𝐔𝐑 𝐀𝐂𝐂𝐎𝐔𝐍𝐓Fast, Available and Reliable for any of the following services 🤳 Recovery of lost funds🤳 Facebook Hack🤳 WhatsApp Hack 🤳 Instagram Hack🤳 Spying🤳 Windows Hacking🤳 Recover lost wallet 🤳 Credit score trick 🤳 Recover Password🤳 Gmail Hack🤳 SnapChat Hacking 🤳 Cellphone Monitoring 🤳 Tik Tok Hack🤳 Twitter Hack🤳 Lost Phone Tracking🤳 Lost IaptopTracking🤳 Lost Car Tracking🤳 Cloning WhatsApp🤳 Cryptocurrency Wallet🤳 Hacking🤳 Iphone unlock 🤳 Got banned 🤳 Private Number available🤳 Telegram hacking 🤳 Websites hacking 🤳 Hack University 🤳 IOS and Android hack 🤳 Wifi Hacking 🤳 CCTV hacking🤳 Hack Bot Game 🤳 Free fire hack 🤳 Changing of school grades 🤳 Cards 💳hackingNo 🆓 services 🚫WhatsApp +1 3606068592Send a DM https://t.me/BlackHat_Nexus@BlackHat_Nexus
-
 @ 000002de:c05780a7
2025-05-06 20:24:08
@ 000002de:c05780a7
2025-05-06 20:24:08https://www.youtube.com/watch?v=CIMZH7DEPPQ
I really enjoy listening to non-technical people talk about technology when they get the bigger picture impacts and how it relates to our humanity.
I was reminded of this video by @k00b's post about an AI generated video of a victim forgiving his killer.
Piper says, "Computers are better at words than you. Than I". But they are machines. They cannot feel. They cannot have emotion.
This people honors me with their lips, but their heart is far from me
~ Matthew 15:8
Most of us hate it when people are fake with us. When they say things they don't mean. When they say things just to get something they want from us. Yet, we are quickly falling into this same trap with technology. Accepting it as real and human. I'm not suggesting we can't use technology but we have to be careful that we do not fall into this mechanical trap and forget what makes humans special.
We are emotional and spiritual beings. Though AI didn't exist during the times Jesus walked the earth read the verse above in a broader context.
Then Pharisees and scribes came to Jesus from Jerusalem and said, “Why do your disciples break the tradition of the elders? For they do not wash their hands when they eat.” He answered them, “And why do you break the commandment of God for the sake of your tradition? For God commanded, ‘Honor your father and your mother,’ and, ‘Whoever reviles father or mother must surely die.’ But you say, ‘If anyone tells his father or his mother, “What you would have gained from me is given to God,” he need not honor his father.’ So for the sake of your tradition you have made void the word of God. You hypocrites! Well did Isaiah prophesy of you, when he said:
“‘This people honors me with their lips,
but their heart is far from me;
in vain do they worship me,
teaching as doctrines the commandments of men.’”
Empty words. Words without meaning because they are not from a pure desire and love. You may not be a Christian but don't miss the significance of this. There is a value in being real. Sharing true emotion and heart. Don't fall into the trap of the culture of lies that surrounds us. I would rather hear true words with mistakes and less eloquence any day over something fake. I would rather share a real moment with the ones I love than a million fake moments. Embrace the messy imperfect but real world.
originally posted at https://stacker.news/items/973324
-
 @ 40b9c85f:5e61b451
2025-04-24 15:27:02
@ 40b9c85f:5e61b451
2025-04-24 15:27:02Introduction
Data Vending Machines (DVMs) have emerged as a crucial component of the Nostr ecosystem, offering specialized computational services to clients across the network. As defined in NIP-90, DVMs operate on an apparently simple principle: "data in, data out." They provide a marketplace for data processing where users request specific jobs (like text translation, content recommendation, or AI text generation)
While DVMs have gained significant traction, the current specification faces challenges that hinder widespread adoption and consistent implementation. This article explores some ideas on how we can apply the reflection pattern, a well established approach in RPC systems, to address these challenges and improve the DVM ecosystem's clarity, consistency, and usability.
The Current State of DVMs: Challenges and Limitations
The NIP-90 specification provides a broad framework for DVMs, but this flexibility has led to several issues:
1. Inconsistent Implementation
As noted by hzrd149 in "DVMs were a mistake" every DVM implementation tends to expect inputs in slightly different formats, even while ostensibly following the same specification. For example, a translation request DVM might expect an event ID in one particular format, while an LLM service could expect a "prompt" input that's not even specified in NIP-90.
2. Fragmented Specifications
The DVM specification reserves a range of event kinds (5000-6000), each meant for different types of computational jobs. While creating sub-specifications for each job type is being explored as a possible solution for clarity, in a decentralized and permissionless landscape like Nostr, relying solely on specification enforcement won't be effective for creating a healthy ecosystem. A more comprehensible approach is needed that works with, rather than against, the open nature of the protocol.
3. Ambiguous API Interfaces
There's no standardized way for clients to discover what parameters a specific DVM accepts, which are required versus optional, or what output format to expect. This creates uncertainty and forces developers to rely on documentation outside the protocol itself, if such documentation exists at all.
The Reflection Pattern: A Solution from RPC Systems
The reflection pattern in RPC systems offers a compelling solution to many of these challenges. At its core, reflection enables servers to provide metadata about their available services, methods, and data types at runtime, allowing clients to dynamically discover and interact with the server's API.
In established RPC frameworks like gRPC, reflection serves as a self-describing mechanism where services expose their interface definitions and requirements. In MCP reflection is used to expose the capabilities of the server, such as tools, resources, and prompts. Clients can learn about available capabilities without prior knowledge, and systems can adapt to changes without requiring rebuilds or redeployments. This standardized introspection creates a unified way to query service metadata, making tools like
grpcurlpossible without requiring precompiled stubs.How Reflection Could Transform the DVM Specification
By incorporating reflection principles into the DVM specification, we could create a more coherent and predictable ecosystem. DVMs already implement some sort of reflection through the use of 'nip90params', which allow clients to discover some parameters, constraints, and features of the DVMs, such as whether they accept encryption, nutzaps, etc. However, this approach could be expanded to provide more comprehensive self-description capabilities.
1. Defined Lifecycle Phases
Similar to the Model Context Protocol (MCP), DVMs could benefit from a clear lifecycle consisting of an initialization phase and an operation phase. During initialization, the client and DVM would negotiate capabilities and exchange metadata, with the DVM providing a JSON schema containing its input requirements. nip-89 (or other) announcements can be used to bootstrap the discovery and negotiation process by providing the input schema directly. Then, during the operation phase, the client would interact with the DVM according to the negotiated schema and parameters.
2. Schema-Based Interactions
Rather than relying on rigid specifications for each job type, DVMs could self-advertise their schemas. This would allow clients to understand which parameters are required versus optional, what type validation should occur for inputs, what output formats to expect, and what payment flows are supported. By internalizing the input schema of the DVMs they wish to consume, clients gain clarity on how to interact effectively.
3. Capability Negotiation
Capability negotiation would enable DVMs to advertise their supported features, such as encryption methods, payment options, or specialized functionalities. This would allow clients to adjust their interaction approach based on the specific capabilities of each DVM they encounter.
Implementation Approach
While building DVMCP, I realized that the RPC reflection pattern used there could be beneficial for constructing DVMs in general. Since DVMs already follow an RPC style for their operation, and reflection is a natural extension of this approach, it could significantly enhance and clarify the DVM specification.
A reflection enhanced DVM protocol could work as follows: 1. Discovery: Clients discover DVMs through existing NIP-89 application handlers, input schemas could also be advertised in nip-89 announcements, making the second step unnecessary. 2. Schema Request: Clients request the DVM's input schema for the specific job type they're interested in 3. Validation: Clients validate their request against the provided schema before submission 4. Operation: The job proceeds through the standard NIP-90 flow, but with clearer expectations on both sides
Parallels with Other Protocols
This approach has proven successful in other contexts. The Model Context Protocol (MCP) implements a similar lifecycle with capability negotiation during initialization, allowing any client to communicate with any server as long as they adhere to the base protocol. MCP and DVM protocols share fundamental similarities, both aim to expose and consume computational resources through a JSON-RPC-like interface, albeit with specific differences.
gRPC's reflection service similarly allows clients to discover service definitions at runtime, enabling generic tools to work with any gRPC service without prior knowledge. In the REST API world, OpenAPI/Swagger specifications document interfaces in a way that makes them discoverable and testable.
DVMs would benefit from adopting these patterns while maintaining the decentralized, permissionless nature of Nostr.
Conclusion
I am not attempting to rewrite the DVM specification; rather, explore some ideas that could help the ecosystem improve incrementally, reducing fragmentation and making the ecosystem more comprehensible. By allowing DVMs to self describe their interfaces, we could maintain the flexibility that makes Nostr powerful while providing the structure needed for interoperability.
For developers building DVM clients or libraries, this approach would simplify consumption by providing clear expectations about inputs and outputs. For DVM operators, it would establish a standard way to communicate their service's requirements without relying on external documentation.
I am currently developing DVMCP following these patterns. Of course, DVMs and MCP servers have different details; MCP includes capabilities such as tools, resources, and prompts on the server side, as well as 'roots' and 'sampling' on the client side, creating a bidirectional way to consume capabilities. In contrast, DVMs typically function similarly to MCP tools, where you call a DVM with an input and receive an output, with each job type representing a different categorization of the work performed.
Without further ado, I hope this article has provided some insight into the potential benefits of applying the reflection pattern to the DVM specification.
-
 @ b6dcdddf:dfee5ee7
2025-05-06 15:58:23
@ b6dcdddf:dfee5ee7
2025-05-06 15:58:23You can now fund projects on Geyser using Credit Cards, Apple Pay, Bank Transfers, and more.
The best part: 🧾 You pay in fiat and ⚡️ the creator receives Bitcoin.
You heard it right! Let's dive in 👇
First, how does it work? For contributors, it's easy! Once the project creator has verified their identity, anyone can contribute with fiat methods. Simply go through the usual contribution flow and select 'Pay with Fiat'. The first contribution is KYC-free.
Why does this matter? 1. Many Bitcoiners don't want to spend their Bitcoin: 👉 Number go up (NgU) 👉 Capital gains taxes With fiat contributions, there's no more excuse to contribute towards Bitcoin builders and creators! 2. Non-bitcoin holders want to support projects too. If someone loves your mission but only has a debit card, they used to be stuck. Now? They can back your Bitcoin project with familiar fiat tools. Now, they can do it all through Geyser!
So, why swap fiat into Bitcoin? Because Bitcoin is borderless. Fiat payouts are limited to certain countries, banks, and red tape. By auto-swapping fiat to Bitcoin, we ensure: 🌍 Instant payouts to creators all around the world ⚡️ No delays or restrictions 💥 Every contribution is also a silent Bitcoin buy
How to enable Fiat contributions If you’re a creator, it’s easy: - Go to your Dashboard → Wallet - Click “Enable Fiat Contributions” - Complete a quick ID verification (required by our payment provider) ✅ That’s it — your project is now open to global fiat supporters.
Supporting Bitcoin adoption At Geyser, our mission is to empower Bitcoin creators and builders. Adding fiat options amplifies our mission. It brings more people into the ecosystem while staying true to what we believe: ⚒️ Build on Bitcoin 🌱 Fund impactful initiatives 🌎 Enable global participation
**Support projects with fiat now! ** We've compiled a list of projects that currently have fiat contributions enabled. If you've been on the fence to support them because you didn't want to spend your Bitcoin, now's the time to do your first contribution!
Education - Citadel Dispatch: https://geyser.fund/project/citadel - @FREEMadeiraOrg: https://geyser.fund/project/freemadeira - @MyfirstBitcoin_: https://geyser.fund/project/miprimerbitcoin
Circular Economies - @BitcoinEkasi: https://geyser.fund/project/bitcoinekasi - Madagascar Bitcoin: https://geyser.fund/project/madagasbit - @BitcoinChatt : https://geyser.fund/project/bitcoinchatt - Uganda Gayaza BTC Market: https://geyser.fund/project/gayazabtcmarket
Activism - Education Bitcoin Channel: https://geyser.fund/project/streamingsats
Sports - The Sats Fighter Journey: https://geyser.fund/project/thesatsfighterjourney
Culture - Bitcoin Tarot Cards: https://geyser.fund/project/bitcointarotcard
originally posted at https://stacker.news/items/973003
-
 @ c631e267:c2b78d3e
2025-04-18 15:53:07
@ c631e267:c2b78d3e
2025-04-18 15:53:07Verstand ohne Gefühl ist unmenschlich; \ Gefühl ohne Verstand ist Dummheit. \ Egon Bahr
Seit Jahren werden wir darauf getrimmt, dass Fakten eigentlich gefühlt seien. Aber nicht alles ist relativ und nicht alles ist nach Belieben interpretierbar. Diese Schokoladenhasen beispielsweise, die an Ostern in unseren Gefilden typisch sind, «ostern» zwar nicht, sondern sie sitzen in der Regel, trotzdem verwandelt sie das nicht in «Sitzhasen».
Nichts soll mehr gelten, außer den immer invasiveren Gesetzen. Die eigenen Traditionen und Wurzeln sind potenziell «pfui», um andere Menschen nicht auszuschließen, aber wir mögen uns toleranterweise an die fremden Symbole und Rituale gewöhnen. Dabei ist es mir prinzipiell völlig egal, ob und wann jemand ein Fastenbrechen feiert, am Karsamstag oder jedem anderen Tag oder nie – aber bitte freiwillig.
Und vor allem: Lasst die Finger von den Kindern! In Bern setzten kürzlich Demonstranten ein Zeichen gegen die zunehmende Verbreitung woker Ideologie im Bildungssystem und forderten ein Ende der sexuellen Indoktrination von Schulkindern.
Wenn es nicht wegen des heiklen Themas Migration oder wegen des Regenbogens ist, dann wegen des Klimas. Im Rahmen der «Netto Null»-Agenda zum Kampf gegen das angeblich teuflische CO2 sollen die Menschen ihre Ernährungsgewohnheiten komplett ändern. Nach dem Willen von Produzenten synthetischer Lebensmittel, wie Bill Gates, sollen wir baldmöglichst praktisch auf Fleisch und alle Milchprodukte wie Milch und Käse verzichten. Ein lukratives Geschäftsmodell, das neben der EU aktuell auch von einem britischen Lobby-Konsortium unterstützt wird.
Sollten alle ideologischen Stricke zu reißen drohen, ist da immer noch «der Putin». Die Unions-Europäer offenbaren sich dabei ständig mehr als Vertreter der Rüstungsindustrie. Allen voran zündelt Deutschland an der Kriegslunte, angeführt von einem scheinbar todesmutigen Kanzlerkandidaten Friedrich Merz. Nach dessen erneuter Aussage, «Taurus»-Marschflugkörper an Kiew liefern zu wollen, hat Russland eindeutig klargestellt, dass man dies als direkte Kriegsbeteiligung werten würde – «mit allen sich daraus ergebenden Konsequenzen für Deutschland».
Wohltuend sind Nachrichten über Aktivitäten, die sich der allgemeinen Kriegstreiberei entgegenstellen oder diese öffentlich hinterfragen. Dazu zählt auch ein Kongress kritischer Psychologen und Psychotherapeuten, der letzte Woche in Berlin stattfand. Die vielen Vorträge im Kontext von «Krieg und Frieden» deckten ein breites Themenspektrum ab, darunter Friedensarbeit oder die Notwendigkeit einer «Pädagogik der Kriegsuntüchtigkeit».
Der heutige «stille Freitag», an dem Christen des Leidens und Sterbens von Jesus gedenken, ist vielleicht unabhängig von jeder religiösen oder spirituellen Prägung eine passende Einladung zur Reflexion. In der Ruhe liegt die Kraft. In diesem Sinne wünsche ich Ihnen frohe Ostertage!
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ c1e9ab3a:9cb56b43
2025-05-06 14:05:40
@ c1e9ab3a:9cb56b43
2025-05-06 14:05:40If you're an engineer stepping into the Bitcoin space from the broader crypto ecosystem, you're probably carrying a mental model shaped by speed, flexibility, and rapid innovation. That makes sense—most blockchain platforms pride themselves on throughput, programmability, and dev agility.
But Bitcoin operates from a different set of first principles. It’s not competing to be the fastest network or the most expressive smart contract platform. It’s aiming to be the most credible, neutral, and globally accessible value layer in human history.
Here’s why that matters—and why Bitcoin is not just an alternative crypto asset, but a structural necessity in the global financial system.
1. Bitcoin Fixes the Triffin Dilemma—Not With Policy, But Protocol
The Triffin Dilemma shows us that any country issuing the global reserve currency must run persistent deficits to supply that currency to the world. That’s not a flaw of bad leadership—it’s an inherent contradiction. The U.S. must debase its own monetary integrity to meet global dollar demand. That’s a self-terminating system.
Bitcoin sidesteps this entirely by being:
- Non-sovereign – no single nation owns it
- Hard-capped – no central authority can inflate it
- Verifiable and neutral – anyone with a full node can enforce the rules
In other words, Bitcoin turns global liquidity into an engineering problem, not a political one. No other system, fiat or crypto, has achieved that.
2. Bitcoin’s “Ossification” Is Intentional—and It's a Feature
From the outside, Bitcoin development may look sluggish. Features are slow to roll out. Code changes are conservative. Consensus rules are treated as sacred.
That’s the point.
When you’re building the global monetary base layer, stability is not a weakness. It’s a prerequisite. Every other financial instrument, app, or protocol that builds on Bitcoin depends on one thing: assurance that the base layer won’t change underneath them without extreme scrutiny.
So-called “ossification” is just another term for predictability and integrity. And when the market does demand change (SegWit, Taproot), Bitcoin’s soft-fork governance process has proven capable of deploying it safely—without coercive central control.
3. Layered Architecture: Throughput Is Not a Base Layer Concern
You don’t scale settlement at the base layer. You build layered systems. Just as TCP/IP doesn't need to carry YouTube traffic directly, Bitcoin doesn’t need to process every microtransaction.
Instead, it anchors:
- Lightning (fast payments)
- Fedimint (community custody)
- Ark (privacy + UTXO compression)
- Statechains, sidechains, and covenants (coming evolution)
All of these inherit Bitcoin’s security and scarcity, while handling volume off-chain, in ways that maintain auditability and self-custody.
4. Universal Assayability Requires Minimalism at the Base Layer
A core design constraint of Bitcoin is that any participant, anywhere in the world, must be able to independently verify the validity of every transaction and block—past and present—without needing permission or relying on third parties.
This property is called assayability—the ability to “test” or verify the authenticity and integrity of received bitcoin, much like verifying the weight and purity of a gold coin.
To preserve this:
- The base layer must remain resource-light, so running a full node stays accessible on commodity hardware.
- Block sizes must remain small enough to prevent centralization of verification.
- Historical data must remain consistent and tamper-evident, enabling proof chains across time and jurisdiction.
Any base layer that scales by increasing throughput or complexity undermines this fundamental guarantee, making the network more dependent on trust and surveillance infrastructure.
Bitcoin prioritizes global verifiability over throughput—because trustless money requires that every user can check the money they receive.
5. Governance: Not Captured, Just Resistant to Coercion
The current controversy around
OP_RETURNand proposals to limit inscriptions is instructive. Some prominent devs have advocated for changes to block content filtering. Others see it as overreach.Here's what matters:
- No single dev, or team, can force changes into the network. Period.
- Bitcoin Core is not “the source of truth.” It’s one implementation. If it deviates from market consensus, it gets forked, sidelined, or replaced.
- The economic majority—miners, users, businesses—enforce Bitcoin’s rules, not GitHub maintainers.
In fact, recent community resistance to perceived Core overreach only reinforces Bitcoin’s resilience. Engineers who posture with narcissistic certainty, dismiss dissent, or attempt to capture influence are routinely neutralized by the market’s refusal to upgrade or adopt forks that undermine neutrality or openness.
This is governance via credible neutrality and negative feedback loops. Power doesn’t accumulate in one place. It’s constantly checked by the network’s distributed incentives.
6. Bitcoin Is Still in Its Infancy—And That’s a Good Thing
You’re not too late. The ecosystem around Bitcoin—especially L2 protocols, privacy tools, custody innovation, and zero-knowledge integrations—is just beginning.
If you're an engineer looking for:
- Systems with global scale constraints
- Architectures that optimize for integrity, not speed
- Consensus mechanisms that resist coercion
- A base layer with predictable monetary policy
Then Bitcoin is where serious systems engineers go when they’ve outgrown crypto theater.
Take-away
Under realistic, market-aware assumptions—where:
- Bitcoin’s ossification is seen as a stability feature, not inertia,
- Market forces can and do demand and implement change via tested, non-coercive mechanisms,
- Proof-of-work is recognized as the only consensus mechanism resistant to fiat capture,
- Wealth concentration is understood as a temporary distribution effect during early monetization,
- Low base layer throughput is a deliberate design constraint to preserve verifiability and neutrality,
- And innovation is layered by design, with the base chain providing integrity, not complexity...
Then Bitcoin is not a fragile or inflexible system—it is a deliberately minimal, modular, and resilient protocol.
Its governance is not leaderless chaos; it's a negative-feedback structure that minimizes the power of individuals or institutions to coerce change. The very fact that proposals—like controversial OP_RETURN restrictions—can be resisted, forked around, or ignored by the market without breaking the system is proof of decentralized control, not dysfunction.
Bitcoin is an adversarially robust monetary foundation. Its value lies not in how fast it changes, but in how reliably it doesn't—unless change is forced by real, bottom-up demand and implemented through consensus-tested soft forks.
In this framing, Bitcoin isn't a slower crypto. It's the engineering benchmark for systems that must endure, not entertain.
Final Word
Bitcoin isn’t moving slowly because it’s dying. It’s moving carefully because it’s winning. It’s not an app platform or a sandbox. It’s a protocol layer for the future of money.
If you're here because you want to help build that future, you’re in the right place.
nostr:nevent1qqswr7sla434duatjp4m89grvs3zanxug05pzj04asxmv4rngvyv04sppemhxue69uhkummn9ekx7mp0qgs9tc6ruevfqu7nzt72kvq8te95dqfkndj5t8hlx6n79lj03q9v6xcrqsqqqqqp0n8wc2
nostr:nevent1qqsd5hfkqgskpjjq5zlfyyv9nmmela5q67tgu9640v7r8t828u73rdqpr4mhxue69uhkymmnw3ezucnfw33k76tww3ux76m09e3k7mf0qgsvr6dt8ft292mv5jlt7382vje0mfq2ccc3azrt4p45v5sknj6kkscrqsqqqqqp02vjk5
nostr:nevent1qqstrszamvffh72wr20euhrwa0fhzd3hhpedm30ys4ct8dpelwz3nuqpr4mhxue69uhkymmnw3ezucnfw33k76tww3ux76m09e3k7mf0qgs8a474cw4lqmapcq8hr7res4nknar2ey34fsffk0k42cjsdyn7yqqrqsqqqqqpnn3znl
-
 @ ba36d0f7:cd802cba
2025-04-22 20:30:45
@ ba36d0f7:cd802cba
2025-04-22 20:30:45| Pieza | Movimiento | Reglas Especiales | | --------- | ---------------------------------- | --------------------------- | | Peón | 1 casilla adelante (o 2 al inicio) | Captura al paso, coronación | | Torre | Líneas rectas | Enroque | | Caballo | En "L" (2+1) | Salta piezas | | Alfil | Diagonales | Atrapado en un color | | Dama | Cualquier dirección | Ninguna | | Rey | 1 casilla en cualquier dirección | Enroque, jaque mate |
1. Peón (♙ / ♟️)
- Mueve: 1 casilla adelante (o 2 en su primer movimiento).

- Captura: En diagonal (1 casilla).
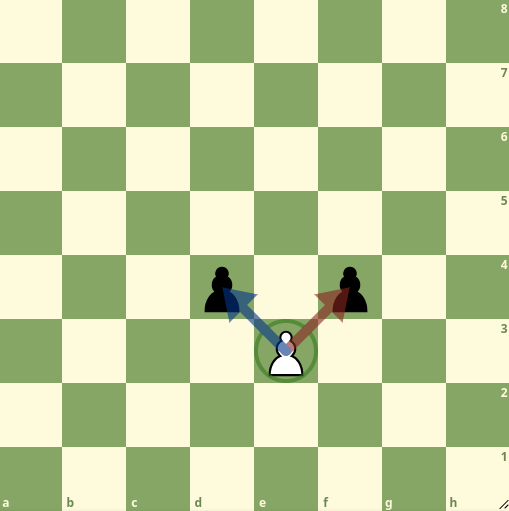 > Especial:
>- Captura al paso: Si un peón rival avanza 2 casillas, puedes capturarlo como si hubiera movido 1.
> - Coronación: Al llegar a la 8ª fila, se convierte en cualquier pieza (¡usualmente Dama!).
> Especial:
>- Captura al paso: Si un peón rival avanza 2 casillas, puedes capturarlo como si hubiera movido 1.
> - Coronación: Al llegar a la 8ª fila, se convierte en cualquier pieza (¡usualmente Dama!).
2. Torre (♖ / ♜)
- Mueve: Líneas rectas (sin límite de casillas).

- Especial: Participa en el enroque.
3. Caballo (♘ / ♞)
-
Mueve: En "L" (2 casillas en una dirección + 1 perpendicular).
-
Única pieza que salta sobre otras.
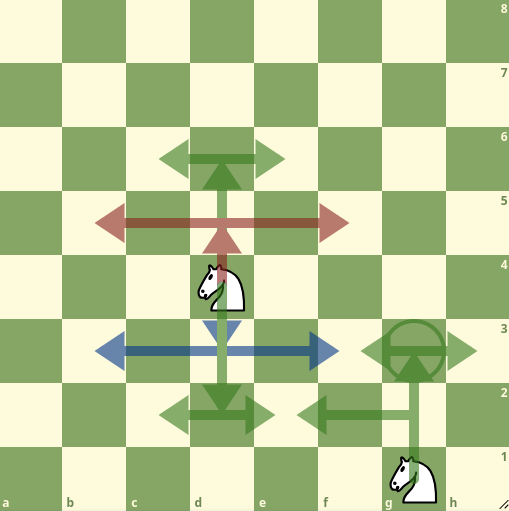
4. Alfil (♗ / ♝)
-
Mueve: Diagonales (sin límite).
-
Siempre permanece en el mismo color de casilla.

5. Dama (♕ / ♛)
- Mueve: Cualquier dirección (recto o diagonal).

- ¡La pieza más poderosa!
6. Rey (♔ / ♚)
- Mueve: 1 casilla en cualquier dirección.

Especial:
- Enroque: Cambia de lugar con una torre (si no hay obstáculos/jaques). - Jaque mate: Pierde si queda atrapado sin escapatoria.
Cómo mover
-
Un movimiento por turno.
-
Elige tu pieza y colócala en una casilla legal.
-
Solo tu color: Blancas mueven primero, luego negras, alternando.
-
No pasar: Debes mover si es tu turno.
Cómo capturar ("comer")
-
Ocupa la casilla de una pieza rival: Reemplázala con tu pieza.
-
Peones capturan solo en diagonal (no de frente).
-
Los reyes no pueden ser capturados (el jaque mate termina el juego).
✔ Jaque: Ataca al rey enemigo (debe escapar en su siguiente turno).
❌ Ilegal: Mover a jaque o dejar a tu rey en jaque.
Movimientos especiales
|Movimiento|Regla Clave|Notación| |---|---|---| |Enroque|Rey + torre, sin movimientos previos|
0-0| |Coronación|Peón→cualquier pieza en 8ª fila|e8=D| |Captura al paso|Captura un peón que avanzó 2 casillas|exd6 a.p.|
1. Enroque ("La escapatoria del rey")
-
Qué: Rey y torre se mueven juntos en un turno.
Cómo: -
Rey mueve 2 casillas hacia una torre.
-
Torre "salta" al lado opuesto del rey.

Reglas: - Sin jaques: El rey no puede estar en jaque ni pasar por casillas atacadas. - Sin movimientos previos: Ni el rey ni esa torre deben haberse movido antes.
Tipos:
- Corto (lado del rey, rápido):0-0- Largo (lado de la dama, seguro):0-0-0
2. Coronación ("Coronar")
-
Qué: Peón llega a la 8ª fila → se convierte en cualquier pieza (usualmente Dama).
-
Cómo: Reemplaza el peón (incluso si ya tienes esa pieza).
Dato curioso: Puedes tener 9 damas (1 original + 8 coronaciones).
Ejemplo: Peón en h8 se convierte en Dama →h8=D.
3. Captura al paso (Del francés "en passant")
-
Cuándo: Un peón rival avanza 2 casillas y queda al lado del tuyo.
-
Cómo: Captúralo en diagonal (como si hubiera movido 1 casilla).

Regla: Debes hacerlo inmediatamente (solo en el turno siguiente)
Recurso digitales
Guia para principiantes - Lichess.org https://lichess.org/study/Hmb28fbv/QRyxzgre
Ajedrez desde cero - Youtube.com https://www.youtube.com/watch?v=YPf9fSY_K2k&list=PLWgqlpb234bHv38g6zXoi3WIJJonzZSAl&index=8
- Mueve: 1 casilla adelante (o 2 en su primer movimiento).
-
 @ 005bc4de:ef11e1a2
2025-05-06 11:54:14
@ 005bc4de:ef11e1a2
2025-05-06 11:54:14May 6 marks my "Nostr birthday." This means I've been on Nostr for two years now. See my initial "Running nostr" note timestamped and archived on the Hive blockchain at https://peakd.com/bitcoin/@crrdlx/running-nostr
Two years ago, I really had no idea what Nostr was. I was asking, "What is this Nostr thing?"
And, I had no idea what I was doing then while using the front end clients. The clients were clunky and since the protocol was rather plastic (still kinda is). As evidence to my ignorance, the spinning wheels on Coracle.social just kept spinning. I didn't realize that since I was only following two people, one being myself, there was nothing to load from relays except my one "Running nostr" note. Hence, the Coracle wheels just spun in their mesmerizing manner. At least they're soothing to watch.
Yet, despite my ignorance, I had an inkling of a notion that Nostr was indeed something different, maybe special. Otherwise, I wouldn't have taken the time to capture an animated gif and make that Hive post to chronicle my first Nostr note.
For fun, I made another "Running nostr" note yesterday using Coracle.social. It still has those muted, earthy tones, but the wheels are not there anymore for long. Coracle, like Nostr, has come a long way in two years. It loads much faster now, which means less wheel spinning. I kind of miss the wheels for some reason, they build the drama and expectation of what might appear.
!HBIT
-
 @ 90c656ff:9383fd4e
2025-05-06 10:32:35
@ 90c656ff:9383fd4e
2025-05-06 10:32:35Bitcoin is a new form of digital money that offers financial freedom and access to a global economy without traditional intermediaries. To take full advantage of this technology, it's important to understand how to buy, store, and use it safely and efficiently. This guide covers the main steps and best practices to incorporate Bitcoin into your daily life, emphasizing how to protect your assets and get the most out of them.
Buying Bitcoin is the first step to participating in its decentralized network. There are several ways to acquire Bitcoin, depending on individual preferences and needs.
- Exchange Platforms:
01 - How it works: Exchanges are online platforms that allow users to buy Bitcoin using traditional currencies like dollars, euros, or reais. 02 - Process: Create an account, complete identity verification (KYC process), and deposit funds to start trading.
Tips: Choose reliable exchanges with strong security and good reputations.
- Bitcoin ATMs:
01 - How it works: Some ATMs allow users to buy Bitcoin with cash or credit cards. 02 - Use: Insert the desired amount, scan your digital wallet, and receive the Bitcoin immediately.
- Peer-to-Peer (P2P) Buying:
01 - How it works: P2P platforms connect buyers and sellers directly, allowing them to negotiate specific terms. 02 - Tips: Check the seller's reputation and use platforms that offer escrow services or transaction guarantees.
Security is crucial when handling Bitcoin. Proper storage protects your funds against loss, hacking, and unauthorized access.
- Digital Wallets:
01 - Definition: A digital wallet is software or a physical device that stores the private keys needed to access your Bitcoin.
Types of Wallets:
01 - Hot wallets: Connected to the internet; suitable for frequent use but more vulnerable to attacks (e.g., mobile apps and web wallets). 02 - Cold wallets: Keep Bitcoin offline; more secure for storing large amounts (e.g., hardware wallets and paper wallets).
- Hardware Wallets:
01 - How they work: Physical devices like Ledger or Trezor store your private keys offline. 02 - Advantages: High security against digital attacks and easy to transport.
- Paper Wallets:
01 - How they work: Involve printing or writing down your private keys on a piece of paper. 02 - Precautions: Store in a safe place, protected from moisture, fire, and unauthorized access.
- Backup and Recovery:
01 - Best practice: Regularly back up your wallet and store your recovery phrase (seed phrase) in a secure location. 02 - Warning: Never share your recovery phrase or private key with anyone.
Using Bitcoin goes beyond investment. It can be used for daily transactions, purchases, and transferring value efficiently.
- Transactions:
01 - How to send Bitcoin: Enter the recipient’s address, the amount to send, and confirm the transaction from your wallet. 02 - Fees: Transaction fees go to miners and may vary based on network demand.
- Purchasing Goods and Services:
01 - Merchants that accept Bitcoin: Many businesses, both physical and online, now accept Bitcoin. Look for the Bitcoin logo or consult updated lists of accepting merchants. 02 - How to pay: Scan the seller’s QR code and send the payment directly from your wallet.
International Transfers: Bitcoin enables fast global transfers, often with lower fees than banks or conventional remittance services.
Bill Payments: In some countries, it's already possible to pay for services and even taxes with Bitcoin, depending on local infrastructure.
- Tips for Using Bitcoin Safely:
01 - Choose trusted wallets and services: Only use well-known, reputable wallets and exchanges. 02 - Enable two-factor authentication (2FA): Activate 2FA to protect your accounts on exchanges and online services. 03 - Don’t leave funds on exchanges: After buying Bitcoin on an exchange, transfer your funds to a wallet you control to reduce the risk of loss from hacks. 04 - Educate yourself: Understanding the basics of Bitcoin and digital security is key to avoiding mistakes and fraud.
In summary, buying, storing, and using Bitcoin might seem complex at first, but it becomes simple and accessible with time. By following best security practices and learning the basics, anyone can benefit from this innovative technology.
Bitcoin is not just a financial option; it’s a powerful tool that supports economic freedom and access to a global economy. With the right knowledge, you can integrate Bitcoin into your life securely and effectively.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ c631e267:c2b78d3e
2025-04-04 18:47:27
@ c631e267:c2b78d3e
2025-04-04 18:47:27Zwei mal drei macht vier, \ widewidewitt und drei macht neune, \ ich mach mir die Welt, \ widewide wie sie mir gefällt. \ Pippi Langstrumpf
Egal, ob Koalitionsverhandlungen oder politischer Alltag: Die Kontroversen zwischen theoretisch verschiedenen Parteien verschwinden, wenn es um den Kampf gegen politische Gegner mit Rückenwind geht. Wer den Alteingesessenen die Pfründe ernsthaft streitig machen könnte, gegen den werden nicht nur «Brandmauern» errichtet, sondern der wird notfalls auch strafrechtlich verfolgt. Doppelstandards sind dabei selbstverständlich inklusive.
In Frankreich ist diese Woche Marine Le Pen wegen der Veruntreuung von EU-Geldern von einem Gericht verurteilt worden. Als Teil der Strafe wurde sie für fünf Jahre vom passiven Wahlrecht ausgeschlossen. Obwohl das Urteil nicht rechtskräftig ist – Le Pen kann in Berufung gehen –, haben die Richter das Verbot, bei Wahlen anzutreten, mit sofortiger Wirkung verhängt. Die Vorsitzende des rechtsnationalen Rassemblement National (RN) galt als aussichtsreiche Kandidatin für die Präsidentschaftswahl 2027.
Das ist in diesem Jahr bereits der zweite gravierende Fall von Wahlbeeinflussung durch die Justiz in einem EU-Staat. In Rumänien hatte Călin Georgescu im November die erste Runde der Präsidentenwahl überraschend gewonnen. Das Ergebnis wurde später annulliert, die behauptete «russische Wahlmanipulation» konnte jedoch nicht bewiesen werden. Die Kandidatur für die Wahlwiederholung im Mai wurde Georgescu kürzlich durch das Verfassungsgericht untersagt.
Die Veruntreuung öffentlicher Gelder muss untersucht und geahndet werden, das steht außer Frage. Diese Anforderung darf nicht selektiv angewendet werden. Hingegen mussten wir in der Vergangenheit bei ungleich schwerwiegenderen Fällen von (mutmaßlichem) Missbrauch ganz andere Vorgehensweisen erleben, etwa im Fall der heutigen EZB-Chefin Christine Lagarde oder im «Pfizergate»-Skandal um die Präsidentin der EU-Kommission Ursula von der Leyen.
Wenngleich derartige Angelegenheiten formal auf einer rechtsstaatlichen Grundlage beruhen mögen, so bleibt ein bitterer Beigeschmack. Es stellt sich die Frage, ob und inwieweit die Justiz politisch instrumentalisiert wird. Dies ist umso interessanter, als die Gewaltenteilung einen essenziellen Teil jeder demokratischen Ordnung darstellt, während die Bekämpfung des politischen Gegners mit juristischen Mitteln gerade bei den am lautesten rufenden Verteidigern «unserer Demokratie» populär zu sein scheint.
Die Delegationen von CDU/CSU und SPD haben bei ihren Verhandlungen über eine Regierungskoalition genau solche Maßnahmen diskutiert. «Im Namen der Wahrheit und der Demokratie» möchte man noch härter gegen «Desinformation» vorgehen und dafür zum Beispiel den Digital Services Act der EU erweitern. Auch soll der Tatbestand der Volksverhetzung verschärft werden – und im Entzug des passiven Wahlrechts münden können. Auf europäischer Ebene würde Friedrich Merz wohl gerne Ungarn das Stimmrecht entziehen.
Der Pegel an Unzufriedenheit und Frustration wächst in großen Teilen der Bevölkerung kontinuierlich. Arroganz, Machtmissbrauch und immer abstrusere Ausreden für offensichtlich willkürliche Maßnahmen werden kaum verhindern, dass den etablierten Parteien die Unterstützung entschwindet. In Deutschland sind die Umfrageergebnisse der AfD ein guter Gradmesser dafür.
[Vorlage Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ a5142938:0ef19da3
2025-05-06 10:31:40
@ a5142938:0ef19da3
2025-05-06 10:31:40Content coming soon.
-
 @ ba36d0f7:cd802cba
2025-04-20 17:58:52
@ ba36d0f7:cd802cba
2025-04-20 17:58:52FABRIC AS TEXTBOOK
Learning to embroider - or to mend - is like studying an ancestral language. Manuals explain the backstitch or sashiko, but fabric never lies: it tears if the tension is weak, and wrinkles if the needle is clumsy.
Theory gives you the alphabet; but practice gives you the syntax of the invisible. How many broken stitches hide behind perfect embroidery? How many mistakes teach us the language of threads?
I. TO MEND IS TO RESIST: THE POLITICAL ACT OF THE NEEDLE
There’s a certain sacred stubbornness in sitting down to mend; like our grandmothers darning our socks until the heel was more patch than original fabric.
And today, in the age of fast fashion, mending is rebellion: a silent "no" to disposability, a resounding "yes" to permanence.
Techniques as Philosophies
-
Japanese sashiko: Visible stitches like proud scars. "What’s broken isn’t hidden—it’s celebrated."

-
Darning: For when pain must be concealed, not erased.

-
Free embroidery: Where repair becomes art and mending, a language.

 Every stitch is a pact: "I care for you because you exist."
Every stitch is a pact: "I care for you because you exist."And isn’t this, too, what mestizaje means? To take the fragmented - fabrics, histories, identities - and reweave them without erasing their origin.
II. EMBROIDERY AS A SELF-TAUGHT MASTER
Learning to embroider is like learning to live: there are no shortcuts. You can read a thousand tutorials, but until you feel the thread resist the needle’s eye or the fabric tense beneath your fingers, knowledge remains abstract.
The Textile Learning Triad
-
Theory that fades (books explain the backstitch, but not how to avoid knots).
-
Practice that stings (fingers get pricked, stitches go crooked).
-
Intuition that blooms (when hands remember the motion on their own).
III. THREADS AND TECHNOLOGY
Malinche, Mesoamerica’s first translator, understood this: some knowledge only transmits through action. We, as 21st-century beings, have a privilege: to blend ancestral tools (needles, threads) with modern ones (YouTube tutorials, digital patterns).
At soma, we explore education beyond canons, and embroidery is the perfect example.
Embroidery teaches us:
-
Discipline (because one loose stitch ruins the design).
-
Creativity (because sometimes you must invent solutions).
-
Legacy (because every thread carries memory).
What are you mending today? A skirt, a habit, a way of learning?
This is the future of education: to dig into the old and hack the new.
IV. INVITATION: STITCHES AND PATIENCE WORKSHOP
This Saturday 26th, at Estudio Malinche, Apaneca - we won’t just teach techniques. We’ll create a collective learning ritual:
-
Bring a torn garment and an empty notebook.
-
Learn sashiko mending (to honor scars) and bookbinding with recycled paper (to chart your path).
-
You’ll leave with ink-stained hands and a heart full of threads.
"Perfection isn’t the goal - persistence is."
Follow us on IG to check out stories & upcoming events: @larutasoma @estudiomalinche
soma #article #mending #workshop #visiblemending #philosophy #resistance #btc #nostr #elsalvador #sashiko #rutadelasflores #apaneca #education #slowfashion #fashion #fastfashion #embroidery #stitching #handmade #diy
-
-
 @ c631e267:c2b78d3e
2025-04-03 07:42:25
@ c631e267:c2b78d3e
2025-04-03 07:42:25Spanien bleibt einer der Vorreiter im europäischen Prozess der totalen Überwachung per Digitalisierung. Seit Mittwoch ist dort der digitale Personalausweis verfügbar. Dabei handelt es sich um eine Regierungs-App, die auf dem Smartphone installiert werden muss und in den Stores von Google und Apple zu finden ist. Per Dekret von Regierungschef Pedro Sánchez und Zustimmung des Ministerrats ist diese Maßnahme jetzt in Kraft getreten.
Mit den üblichen Argumenten der Vereinfachung, des Komforts, der Effizienz und der Sicherheit preist das Innenministerium die «Innovation» an. Auch die Beteuerung, dass die digitale Variante parallel zum physischen Ausweis existieren wird und diesen nicht ersetzen soll, fehlt nicht. Während der ersten zwölf Monate wird «der Neue» noch nicht für alle Anwendungsfälle gültig sein, ab 2026 aber schon.
Dass die ganze Sache auch «Risiken und Nebenwirkungen» haben könnte, wird in den Mainstream-Medien eher selten thematisiert. Bestenfalls wird der Aspekt der Datensicherheit angesprochen, allerdings in der Regel direkt mit dem Regierungsvokabular von den «maximalen Sicherheitsgarantien» abgehandelt. Dennoch gibt es einige weitere Aspekte, die Bürger mit etwas Sinn für Privatsphäre bedenken sollten.
Um sich die digitale Version des nationalen Ausweises besorgen zu können (eine App mit dem Namen MiDNI), muss man sich vorab online registrieren. Dabei wird die Identität des Bürgers mit seiner mobilen Telefonnummer verknüpft. Diese obligatorische fixe Verdrahtung kennen wir von diversen anderen Apps und Diensten. Gleichzeitig ist das die Basis für eine perfekte Lokalisierbarkeit der Person.
Für jeden Vorgang der Identifikation in der Praxis wird später «eine Verbindung zu den Servern der Bundespolizei aufgebaut». Die Daten des Individuums werden «in Echtzeit» verifiziert und im Erfolgsfall von der Polizei signiert zurückgegeben. Das Ergebnis ist ein QR-Code mit zeitlich begrenzter Gültigkeit, der an Dritte weitergegeben werden kann.
Bei derartigen Szenarien sträuben sich einem halbwegs kritischen Staatsbürger die Nackenhaare. Allein diese minimale Funktionsbeschreibung lässt die totale Überwachung erkennen, die damit ermöglicht wird. Jede Benutzung des Ausweises wird künftig registriert, hinterlässt also Spuren. Und was ist, wenn die Server der Polizei einmal kein grünes Licht geben? Das wäre spätestens dann ein Problem, wenn der digitale doch irgendwann der einzig gültige Ausweis ist: Dann haben wir den abschaltbaren Bürger.
Dieser neue Vorstoß der Regierung von Pedro Sánchez ist ein weiterer Schritt in Richtung der «totalen Digitalisierung» des Landes, wie diese Politik in manchen Medien – nicht einmal kritisch, sondern sehr naiv – genannt wird. Ebenso verharmlosend wird auch erwähnt, dass sich das spanische Projekt des digitalen Ausweises nahtlos in die Initiativen der EU zu einer digitalen Identität für alle Bürger sowie des digitalen Euro einreiht.
In Zukunft könnte der neue Ausweis «auch in andere staatliche und private digitale Plattformen integriert werden», wie das Medienportal Cope ganz richtig bemerkt. Das ist die Perspektive.
[Titelbild: Pixabay]
Dazu passend:
Nur Abschied vom Alleinfahren? Monströse spanische Überwachungsprojekte gemäß EU-Norm
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ aa8de34f:a6ffe696
2025-03-31 21:48:50
@ aa8de34f:a6ffe696
2025-03-31 21:48:50In seinem Beitrag vom 30. März 2025 fragt Henning Rosenbusch auf Telegram angesichts zunehmender digitaler Kontrolle und staatlicher Allmacht:
„Wie soll sich gegen eine solche Tyrannei noch ein Widerstand formieren können, selbst im Untergrund? Sehe ich nicht.“\ (Quelle: t.me/rosenbusch/25228)
Er beschreibt damit ein Gefühl der Ohnmacht, das viele teilen: Eine Welt, in der Totalitarismus nicht mehr mit Panzern, sondern mit Algorithmen kommt. Wo Zugriff auf Geld, Meinungsfreiheit und Teilhabe vom Wohlverhalten abhängt. Der Bürger als kontrollierbare Variable im Code des Staates.\ Die Frage ist berechtigt. Doch die Antwort darauf liegt nicht in alten Widerstandsbildern – sondern in einer neuen Realität.
-- Denn es braucht keinen Untergrund mehr. --
Der Widerstand der Zukunft trägt keinen Tarnanzug. Er ist nicht konspirativ, sondern transparent. Nicht bewaffnet, sondern mathematisch beweisbar. Bitcoin steht nicht am Rand dieser Entwicklung – es ist ihr Fundament. Eine Bastion aus physikalischer Realität, spieltheoretischem Schutz und ökonomischer Wahrheit. Es ist nicht unfehlbar, aber unbestechlich. Nicht perfekt, aber immun gegen zentrale Willkür.
Hier entsteht kein „digitales Gegenreich“, sondern eine dezentrale Renaissance. Keine Revolte aus Wut, sondern eine stille Abkehr: von Zwang zu Freiwilligkeit, von Abhängigkeit zu Selbstverantwortung. Diese Revolution führt keine Kriege. Sie braucht keine Führer. Sie ist ein Netzwerk. Jeder Knoten ein Individuum. Jede Entscheidung ein Akt der Selbstermächtigung.
Weltweit wachsen Freiheits-Zitadellen aus dieser Idee: wirtschaftlich autark, digital souverän, lokal verankert und global vernetzt. Sie sind keine Utopien im luftleeren Raum, sondern konkrete Realitäten – angetrieben von Energie, Code und dem menschlichen Wunsch nach Würde.
Der Globalismus alter Prägung – zentralistisch, monopolistisch, bevormundend – wird an seiner eigenen Hybris zerbrechen. Seine Werkzeuge der Kontrolle werden ihn nicht retten. Im Gegenteil: Seine Geister werden ihn verfolgen und erlegen.
Und während die alten Mächte um Erhalt kämpfen, wächst eine neue Welt – nicht im Schatten, sondern im Offenen. Nicht auf Gewalt gebaut, sondern auf Mathematik, Physik und Freiheit.
Die Tyrannei sieht keinen Widerstand.\ Weil sie nicht erkennt, dass er längst begonnen hat.\ Unwiderruflich. Leise. Überall.
-
 @ ba36d0f7:cd802cba
2025-04-16 16:39:58
@ ba36d0f7:cd802cba
2025-04-16 16:39:581. El placer creativo (pero efímero) de las tácticas
Las tácticas en ajedrez son como las golosinas entre comidas: satisfacción inmediata, pero no sustento real. Escoger entre atacar a un alfil o un caballo puede ser como elegir entre helado de vainilla o chocolate - con chispas o sin chispas, cereza o sin cereza....
-
Son libertad dentro de las reglas: el tablero es finito, pero la creatividad no.
-
Reflejan tu estilo: ¿ataques rápidos como un espresso? ¿O finales lentos como un té verde?
2. Dos tipos de tácticas, dos tipos de placeres
-
Sencillas (como un rey descubierto): placeres cotidianos (como un golpe de buena suerte).
-
Complejas (combinaciones de 3+ jugadas): placeres que exigen planificación (como cumplir metas).
3. La advertencia budista: "No confundas el postre con la cena"
El Buddha enseñó que aferrarse a los placeres (kāma-tanha) genera sufrimiento. En ajedrez y en la vida:
-
Las tácticas son golosinas: te dan ventaja, pero no son estrategia.
- Ejemplo: Ganar por un descuido del rival es como heredar dinero; ganar por planificación es como construir un negocio.
-
El equilibrio: Disfruta ese sacrificio de dama espectacular… pero no bases tu juego en ellos. Como saborear un pastel ocasional sin volverse adicto al azúcar.
4. Cómo aplicar esto en el tablero (y en la vida)
✅ Pregúntate siempre:
-
¿Esta táctica es sólida o solo emocionante? (Como diferenciar antojo de hambre real).
-
¿Estoy jugando para ganar… o para impresionar? (El ego es peor enemigo que el rival).
Conclusión: El camino medio (ajedrecístico)
El budismo no pide renunciar a los placeres, sino disfrutarlos sin apego. En el ajedrez:
-
Tácticas = especias: dan sabor, pero no son el plato principal.
-
Estrategia = nutrición: lo que realmente te hace mejor jugador.
♟️ ¿Y tú? ¿Eres de los que prefieren un ataque brillante (aunque riesgoso) o una victoria lenta pero segura?
Recursos en linea
Tácticas - chess.com https://www.chess.com/es/article/view/tacticas-ajedrez
Problemas de ajedrez - chess.com https://www.chess.com/es/puzzles
Tácticas - lichess.org https://lichess.org/study/qgLXlnIF/udsuAudN
ajedrez #somachess #chess #chesselsalvador #budismo #budhism #filosofia #philosophy #apaneca #rutadelasflores #article #longform #articulo
-
-
 @ ba36d0f7:cd802cba
2025-04-16 15:09:25
@ ba36d0f7:cd802cba
2025-04-16 15:09:25What is Checkmate?
Checkmate is the decisive move that ends the game. It occurs when the king is under direct threat (in check) and there’s no legal move to save it: neither capturing the attacking piece, blocking the attack, nor fleeing to a safe square.
Unlike other pieces, the king can never be captured - its downfall marks the end of the game. Thus, when escape is impossible, the game ends immediately. There’s no need to "take" the king; its fate is already sealed.
How to Achieve Checkmate?
It requires:
-
Imminent Threat: One or more pieces attacking the enemy king.

-
Total Blockade: All escape squares controlled by the opponent.

- No Possible Defense: No piece can intercept the attack.

Basic Example: The Back-Rank Mate (with a rook or queen on the last rank, where the king can’t escape due to being blocked by its own pieces).
1. The First Chess Commandment: Seek Checkmate
In every game, each move should begin with an essential question: Is there a checkmate in this position? - for both yourself and your opponent. If not, the game revolves around material advantage or positional control. But this order isn’t arbitrary:
-
A tactical oversight can ruin a dominant position.
-
A missed checkmate means instant defeat.
Classic Example: The Scholar’s Mate (1.e4 e5 2.Bc4 Nc6 3.Qh5 Nf6?? 4.Qxf7#).
 White wins because Black, focused solely on development, ignored the deadly threat.
White wins because Black, focused solely on development, ignored the deadly threat.➡ Reflection: In strategy, as in life, the urgent (survival) precedes the important (victory).
2. The Philosophy of the Board: When Advantages Aren’t Enough
A lone king can evade capture forever if the opponent doesn’t know how to checkmate. Similarly, in human existence, advantages - talent, resources, or opportunities - are worthless if not transformed into decisive actions.
-
What good is controlling the center if you can’t convert it into an attack?
-
What good are privileges if not used to build something meaningful?
Chess, like life, rewards execution - not accumulation.
3. Survival Instinct: Between Attack and Resistance
The fear of defeat triggers visceral reactions: desperate attacks, obsessive defenses, or even premature resignations. But these responses reveal deep truths about human nature:
-
Survival ≠ Violence: A cornered king may shelter behind its pieces, like a strategist choosing patience over confrontation. Is it cowardice or wisdom?
-
The Danger of Ego: Arrogance ("I must win quickly") leads to irreversible mistakes. Humility ("I’ll resist until my opponent errs") can turn certain defeat into salvation.
➡ Reflection: The board doesn’t lie. Every move exposes a player’s deepest instincts: fear, ambition, or temperance.
Online Resources
Check mate patterns - Lichess.org https://lichess.org/practice/checkmates/checkmate-patterns-i/fE4k21MW/9rd7XwOw
Piece check mates - Lichess.org https://lichess.org/practice/checkmates/piece-checkmates-i/BJy6fEDf/8K8FdT6P
Common check mates - Chess.com https://www.chess.com/terms/checkmate-chess
10 fastest check mates - Chess.com https://www.chess.com/article/view/fastest-chess-checkmates
Finding check mates - Chess.com https://www.chess.com/lessons/finding-checkmate
somachess #chess #chesselsalvador #ajedrez #chessphilosophy #philosophy #filosofia #checkmate #longform #article
-
-
 @ e4950c93:1b99eccd
2025-05-06 10:35:37
@ e4950c93:1b99eccd
2025-05-06 10:35:37Qu'est-ce qu'une matière naturelle ? La question fait débat, et chacun-e privilégiera ses propres critères. Voici comment les matières sont classées sur ce site. La liste est régulièrement mise à jour en fonction des produits ajoutés. N'hésitez pas à partager votre avis !
✅ Matières naturelles
Matières d'origine végétale, animale ou minérale, sans transformation chimique altérant leur structure moléculaire.
🌱 Principaux critères : - Biodégradabilité - Non-toxicité - Présence naturelle nécessitant le minimum de transformation
🔍 Liste des matières naturelles : - Bois - Cellulose régénérée (cupra, lyocell, modal, viscose) - Chanvre - Coton - Cuir - Liège - Lin - Laine - Latex naturel, caoutchouc - Métal - Soie - Terre - Verre - … (Autres matières)
⚠️ Bien que "naturelles", ces matières peuvent générer des impacts négatifs selon leurs conditions de production (pollution par pesticides, consommation d’eau excessive, traitement chimique, exploitation animale…). Ces impacts sont mentionnés sur la fiche de chaque matière.
Les versions biologiques de ces matières (sans traitement chimique, maltraitance animale, etc.) sont privilégiées pour référencer les produits sur ce site, tel qu'indiqué sur la fiche de chaque matière (à venir).
Les versions conventionnelles ne sont référencées que tant que lorsqu'il n'a pas encore été trouvé d'alternative plus durable pour cette catégorie de produits.
🚫 Matières non naturelles
Matières synthétiques ou fortement modifiées, souvent issues de la pétrochimie.
📌 Principaux problèmes : - Toxicité et émissions de microplastiques - Dépendance aux énergies fossiles - Mauvaise biodégradabilité
🔍 Liste des matières non naturelles : - Acrylique - Élasthanne, lycra, spandex - Polyamides, nylon - Polyester - Silicone - … (Autres matières)
⚠️ Ces matières ne sont pas admises sur le site. Néanmoins, elles peuvent être présentes dans certains produits référencés lorsque :
- elles sont utilisées en accessoire amovible (ex. : élastiques, boutons… généralement non indiqué dans la composition par la marque) pouvant être retiré pour le recyclage ou compostage, et
- aucune alternative 100 % naturelle n’a encore été identifiée pour cette catégorie de produits.
Dans ce cas, un avertissement est alors affiché sur la fiche du produit.
Cet article est publié sur origine-nature.com 🌐 See this article in English
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 80a6a657:536a97e2
2025-05-06 10:00:48
@ 80a6a657:536a97e2
2025-05-06 10:00:48
The dawn of Bitcoin ushered in a transformative mission: empowering individuals and dismantling centralized power structures that erode personal freedoms. As the world’s first decentralized currency, Bitcoin offers an alternative financial system—one that transcends borders, government control, and corporate interests.
But this mission isn’t just about money. It’s about freedom. It’s about self-sovereignty. And most importantly, it’s a rallying cry for vigilance in an ongoing struggle for the liberation of humanity from systemic oppression. Who better to lead this critical mission than those who have already dedicated their lives to serving and protecting freedom: Veterans.
Freedom: A Lifelong Fight Freedom is neither freely given nor guaranteed—it is earned and fiercely preserved. Veterans understand this intimately. They have endured sacrifice, hardship, and battle in their service to protect the liberties we often take for granted. And today, freedom faces threats from a new frontier: financial manipulation, surveillance, and the centralization of power.
Governments across the globe continue to devalue currencies through inflation, tighten financial surveillance by controlling banking systems, and stifle individual autonomy. These issues underscore the need for a sound financial alternative, one that aligns with the ideals veterans have sworn to uphold. The solution? Bitcoin.
Bitcoin represents the antithesis of centralized control. It is censorship-resistant, immune to monetary debasement, and built upon a trustless, transparent system. It is not merely a currency; it is a tool for human liberation.
Vigilance in Bitcoin Adoption While Bitcoin adoption grows, the journey is far from complete. The powerful status quo—central banks, governments, and financial elites—does not take threats to its systems lightly. These entities work tirelessly to misinform, regulate, and marginalize Bitcoin. This makes sustained vigilance in promoting Bitcoin adoption not just important, but essential.
The failure to remain vigilant could see Bitcoin’s potential diminished through undue regulation, controlled implementation (such as CBDCs—Central Bank Digital Currencies), or a failure to educate people about its benefits. Complacency would mean ceding victory to oppressive systems the world over.
This is why Bitcoin adoption isn’t solely a technological phenomenon—it is an ideological mission. To resist control, to safeguard freedom, and to empower individuals to thrive under self-sovereignty requires the active participation of people across all sectors of society.
Why Veterans Are Uniquely Positioned to Lead Veterans are inherently equipped to lead the charge in the fight for Bitcoin adoption and the broader battle for freedom. Their unique skillsets, shaped by discipline, adaptability, and leadership under pressure, are perfectly suited to this challenge. Here’s why veterans play a pivotal role in this movement: 1. Leadership and Vision: Veterans are natural leaders. They can galvanize communities toward a vision of financial independence, self-sovereignty, and empowerment through Bitcoin. Their experience coordinating efforts—whether on the battlefield or in humanitarian missions—allows them to efficiently communicate the importance of Bitcoin adoption. 2. Commitment to Freedom: The fight for Bitcoin adoption is deeply aligned with the ethos of service members: defending freedom at all costs. Veterans understand that true freedom cannot persist without vigilance, sacrifice, and a commitment to challenging oppressive systems. 3. Trust and Credibility: The military often fosters a level of trust and camaraderie among people. Veterans, therefore, have the clout to introduce Bitcoin to communities that may otherwise view it with skepticism. Their credibility as protectors of freedom gives them an edge in delivering Bitcoin’s message of liberation. 4. Adaptability in Uncertain Environments: Just as they’ve thrived in complex and chaotic environments, veterans are poised to navigate the evolving financial landscape. Bitcoin is still maturing and faces regulatory challenges, technological hurdles, and cultural misunderstandings. Veterans excel at adapting to change and finding solutions in challenging circumstances. 5. Mission-Driven Mindset: Every mission has an objective, and every objective demands clear focus. Veterans approach tasks methodically and with a commitment to success—the same mindset required to bridge the gap between Bitcoin skepticism and widespread adoption.
The Call to Action Veterans, the mission isn’t over. Humanity stands at a crossroads, and freedom is at stake. Bitcoin is not just a disruptive technology; it’s the torchbearer of liberty in a world increasingly dominated by centralized control. It’s time to take the skills, discipline, and passion forged in your service and channel them into this new fight: the fight for financial freedom and independence from a centralized system that has dominated the lives of billions of people for far too long.
Educate yourself about Bitcoin. Learn its nuances, its strengths, and its use cases. Share this knowledge with your communities, help dismantle misconceptions, and shine a light on the real promise of self-sovereignty. Become an anchor of leadership in this decentralized revolution.
For civilians: do not underestimate the importance of this mission. Every individual who adopts Bitcoin drives us one step closer to a world where personal freedom and economic empowerment are accessible to all. Join arms with veterans, thought leaders, and Bitcoin adopters to ensure the torch of liberty burns brightly.
Closing Thoughts Bitcoin is more than a financial revolution—it’s a movement for freedom. Veterans have long stood on the frontline for this cause, and today, they have an opportunity to champion it in a new way. With vigilance, resolve, and determination, humanity can achieve greater levels of freedom. But, as with all efforts to secure liberty, we must remain constantly committed to the mission. Remember: freedom demands eternal vigilance. So does Bitcoin.
Will you answer the call? Together, we can reshape the future as champions of sovereignty and bring the world closer to the ideals we all deserve.
OPERATION BITCOIN is a 501(c)(3) nonprofit on a mission to connect military veterans with Bitcoin.
You can directly support this mission by sharing our publication with a veteran today, zapping this article or donating at www.operationbitcoin.io
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ e4950c93:1b99eccd
2025-05-06 10:32:20
@ e4950c93:1b99eccd
2025-05-06 10:32:20Contenu à venir.
-
 @ 01acb73f:5a8e92a9
2025-05-06 04:27:42
@ 01acb73f:5a8e92a9
2025-05-06 04:27:42O universo dos jogos online está cada vez mais diversificado e atrativo para os brasileiros que buscam entretenimento e adrenalina. Nesse cenário, o Forró777 se destaca como uma plataforma inovadora e completa, oferecendo uma experiência única para quem quer unir diversão, praticidade e chances reais de premiação. Com um ambiente virtual moderno, suporte eficiente e uma grande variedade de jogos, o Forró777 conquistou seu espaço no mercado e vem se tornando a escolha preferida de muitos jogadores.
Uma Plataforma que Fala a Língua do Brasileiro Desde o primeiro acesso, o Forró777 mostra que foi feito pensando no público brasileiro. A interface é amigável, com menus intuitivos e em português, o que facilita a navegação até para iniciantes. A plataforma funciona de forma fluida tanto em computadores quanto em dispositivos móveis, permitindo que o usuário jogue quando e onde quiser.
Outro ponto forte é a segurança. O site conta com tecnologias de criptografia avançadas para proteger as informações dos usuários e garantir transações seguras. Além disso, o suporte ao cliente está disponível 24 horas por dia, sempre pronto para esclarecer dúvidas e resolver qualquer problema com rapidez e eficiência.
Variedade de Jogos para Todos os Gostos O catálogo de jogos do Forro777é um dos mais completos do mercado. Os jogadores podem se divertir com diferentes estilos, desde os clássicos até os mais modernos. Entre os destaques estão os populares jogos de caça-níqueis, com temas variados e gráficos impressionantes. Com rodadas rápidas e animações envolventes, esses jogos são ideais para quem busca entretenimento dinâmico e recompensas atrativas.
Outro sucesso na plataforma são os jogos ao vivo, nos quais o usuário interage em tempo real com apresentadores profissionais e outros participantes. Essa modalidade traz uma imersão maior e faz com que o jogador se sinta em um ambiente real de competição e diversão.
Além disso, o Forró777 também oferece jogos de loteria instantânea, roletas digitais, pôquer online e muito mais. Essa diversidade garante que cada usuário encontre algo que combine com seu estilo e preferências.
Uma Experiência de Jogador Incomparável O grande diferencial do Forró777 está na experiência que ele proporciona. O site não é apenas uma plataforma de jogos, mas sim um ambiente de entretenimento completo. Os bônus e promoções frequentes são um atrativo à parte, com ofertas que incluem giros grátis, prêmios em dinheiro e recompensas exclusivas para novos usuários e jogadores fiéis.
Outro ponto muito elogiado pelos usuários é o programa de fidelidade, que premia jogadores frequentes com vantagens especiais, como atendimento VIP, cashback e bônus personalizados. Isso cria uma sensação de valorização que faz com que o jogador se sinta parte de uma comunidade exclusiva.
Conclusão Se você está em busca de uma plataforma confiável, divertida e com muitas possibilidades de ganhos, o Forró777 é uma excelente escolha. Com sua ampla variedade de jogos, sistema seguro e atendimento dedicado, o site entrega tudo o que o jogador moderno procura. Prepare-se para uma jornada cheia de emoção, recompensas e diversão no Forró777 — onde o ritmo da vitória nunca para!
-
 @ 01acb73f:5a8e92a9
2025-05-06 04:26:54
@ 01acb73f:5a8e92a9
2025-05-06 04:26:54A 9009Bet tem se destacado no cenário de entretenimento online no Brasil por oferecer uma plataforma moderna, segura e recheada de opções para quem busca diversão e oportunidades de ganhos. Com um visual intuitivo, suporte eficiente e uma enorme variedade de jogos, o site atrai tanto iniciantes quanto jogadores experientes em busca de uma experiência dinâmica e empolgante.
Introdução à Plataforma 9009Bet Desde o primeiro acesso, a 9009Bet impressiona por sua interface amigável e bem estruturada. O site é responsivo, funcionando perfeitamente em computadores, tablets e smartphones, o que permite aos usuários jogar onde e quando quiserem. A plataforma investe constantemente em tecnologia para garantir navegação rápida, carregamento ágil dos jogos e total segurança dos dados pessoais e financeiros.
Além disso, a 9009betconta com métodos de pagamento variados e eficientes, incluindo PIX, transferências bancárias e carteiras digitais, o que facilita tanto os depósitos quanto os saques. Tudo isso com a transparência e a confiabilidade que os usuários esperam de uma plataforma de alto nível.
Jogos para Todos os Gostos Um dos maiores atrativos da 9009Bet é a diversidade de jogos disponíveis. A plataforma oferece opções que agradam a todos os estilos e perfis de jogador, com títulos desenvolvidos por fornecedores renomados do mercado internacional. Entre os destaques, estão os jogos de roleta, bacará, blackjack e caça-níqueis — cada um com múltiplas variações e temáticas que vão desde o clássico até o moderno.
Os fãs de jogos com temática de aventura, mitologia ou cultura oriental, por exemplo, encontram opções com gráficos envolventes e trilhas sonoras cativantes. Para quem prefere algo mais direto e rápido, os slots com rodadas relâmpago e bônus instantâneos são uma excelente escolha.
Outro diferencial são os jogos com recursos interativos, onde o jogador pode tomar decisões estratégicas em tempo real, o que eleva ainda mais o nível de imersão e entretenimento.
A Experiência do Jogador no Centro de Tudo Na 9009Bet, a prioridade é garantir que cada jogador se sinta valorizado e bem atendido. Por isso, o site conta com um sistema de suporte ao cliente 24 horas por dia, sete dias por semana. Os atendentes são treinados para solucionar dúvidas e problemas de forma ágil e educada, seja por chat ao vivo, e-mail ou outros canais de comunicação.
A plataforma também promove campanhas promocionais regulares, com bônus de boas-vindas, rodadas grátis e sorteios exclusivos para membros cadastrados. Esses incentivos aumentam as chances de ganhar e proporcionam um ambiente ainda mais animado.
Para os jogadores mais ativos, a 9009Bet oferece um sistema de recompensas e benefícios VIP, que inclui acesso a eventos especiais, atendimento personalizado e promoções exclusivas.
Conclusão A 9009Bet se consolida como uma das melhores plataformas de entretenimento digital no Brasil, combinando inovação, variedade de jogos e uma experiência centrada no usuário. Seja você um novato curioso ou um jogador veterano, encontrará na 9009Bet um ambiente seguro, justo e repleto de diversão. Experimente e descubra por que tantos brasileiros estão escolhendo a 9009Bet como seu lugar favorito para jogar e se entreter.
-
 @ 9223d2fa:b57e3de7
2025-04-15 02:54:00
@ 9223d2fa:b57e3de7
2025-04-15 02:54:0012,600 steps
-
 @ c631e267:c2b78d3e
2025-03-31 07:23:05
@ c631e267:c2b78d3e
2025-03-31 07:23:05Der Irrsinn ist bei Einzelnen etwas Seltenes – \ aber bei Gruppen, Parteien, Völkern, Zeiten die Regel. \ Friedrich Nietzsche
Erinnern Sie sich an die Horrorkomödie «Scary Movie»? Nicht, dass ich diese Art Filme besonders erinnerungswürdig fände, aber einige Szenen daraus sind doch gewissermaßen Klassiker. Dazu zählt eine, die das Verhalten vieler Protagonisten in Horrorfilmen parodiert, wenn sie in Panik flüchten. Welchen Weg nimmt wohl die Frau in der Situation auf diesem Bild?

Diese Szene kommt mir automatisch in den Sinn, wenn ich aktuelle Entwicklungen in Europa betrachte. Weitreichende Entscheidungen gehen wider jede Logik in die völlig falsche Richtung. Nur ist das hier alles andere als eine Komödie, sondern bitterernst. Dieser Horror ist leider sehr real.
Die Europäische Union hat sich selbst über Jahre konsequent in eine Sackgasse manövriert. Sie hat es versäumt, sich und ihre Politik selbstbewusst und im Einklang mit ihren Wurzeln auf dem eigenen Kontinent zu positionieren. Stattdessen ist sie in blinder Treue den vermeintlichen «transatlantischen Freunden» auf ihrem Konfrontationskurs gen Osten gefolgt.
In den USA haben sich die Vorzeichen allerdings mittlerweile geändert, und die einst hoch gelobten «Freunde und Partner» erscheinen den europäischen «Führern» nicht mehr vertrauenswürdig. Das ist spätestens seit der Münchner Sicherheitskonferenz, der Rede von Vizepräsident J. D. Vance und den empörten Reaktionen offensichtlich. Große Teile Europas wirken seitdem wie ein aufgescheuchter Haufen kopfloser Hühner. Orientierung und Kontrolle sind völlig abhanden gekommen.
Statt jedoch umzukehren oder wenigstens zu bremsen und vielleicht einen Abzweig zu suchen, geben die Crash-Piloten jetzt auf dem Weg durch die Sackgasse erst richtig Gas. Ja sie lösen sogar noch die Sicherheitsgurte und deaktivieren die Airbags. Den vor Angst dauergelähmten Passagieren fällt auch nichts Besseres ein und so schließen sie einfach die Augen. Derweil übertrumpfen sich die Kommentatoren des Events gegenseitig in sensationslüsterner «Berichterstattung».
Wie schon die deutsche Außenministerin mit höchsten UN-Ambitionen, Annalena Baerbock, proklamiert auch die Europäische Kommission einen «Frieden durch Stärke». Zu dem jetzt vorgelegten, selbstzerstörerischen Fahrplan zur Ankurbelung der Rüstungsindustrie, genannt «Weißbuch zur europäischen Verteidigung – Bereitschaft 2030», erklärte die Kommissionspräsidentin, die «Ära der Friedensdividende» sei längst vorbei. Soll das heißen, Frieden bringt nichts ein? Eine umfassende Zusammenarbeit an dauerhaften europäischen Friedenslösungen steht demnach jedenfalls nicht zur Debatte.
Zusätzlich brisant ist, dass aktuell «die ganze EU von Deutschen regiert wird», wie der EU-Parlamentarier und ehemalige UN-Diplomat Michael von der Schulenburg beobachtet hat. Tatsächlich sitzen neben von der Leyen und Strack-Zimmermann noch einige weitere Deutsche in – vor allem auch in Krisenzeiten – wichtigen Spitzenposten der Union. Vor dem Hintergrund der Kriegstreiberei in Deutschland muss eine solche Dominanz mindestens nachdenklich stimmen.
Ihre ursprünglichen Grundwerte wie Demokratie, Freiheit, Frieden und Völkerverständigung hat die EU kontinuierlich in leere Worthülsen verwandelt. Diese werden dafür immer lächerlicher hochgehalten und beschworen.
Es wird dringend Zeit, dass wir, der Souverän, diesem erbärmlichen und gefährlichen Trauerspiel ein Ende setzen und die Fäden selbst in die Hand nehmen. In diesem Sinne fordert uns auch das «European Peace Project» auf, am 9. Mai im Rahmen eines Kunstprojekts den Frieden auszurufen. Seien wir dabei!
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 66675158:1b644430
2025-03-23 11:39:41
@ 66675158:1b644430
2025-03-23 11:39:41I don't believe in "vibe coding" – it's just the newest Silicon Valley fad trying to give meaning to their latest favorite technology, LLMs. We've seen this pattern before with blockchain, when suddenly Non Fungible Tokens appeared, followed by Web3 startups promising to revolutionize everything from social media to supply chains. VCs couldn't throw money fast enough at anything with "decentralized" (in name only) in the pitch deck. Andreessen Horowitz launched billion-dollar crypto funds, while Y Combinator batches filled with blockchain startups promising to be "Uber for X, but on the blockchain."
The metaverse mania followed, with Meta betting its future on digital worlds where we'd supposedly hang out as legless avatars. Decentralized (in name only) autonomous organizations emerged as the next big thing – supposedly democratic internet communities that ended up being the next scam for quick money.
Then came the inevitable collapse. The FTX implosion in late 2022 revealed fraud, Luna/Terra's death spiral wiped out billions (including my ten thousand dollars), while Celsius and BlockFi froze customer assets before bankruptcy.
By 2023, crypto winter had fully set in. The SEC started aggressive enforcement actions, while users realized that blockchain technology had delivered almost no practical value despite a decade of promises.
Blockchain's promises tapped into fundamental human desires – decentralization resonated with a generation disillusioned by traditional institutions. Evangelists presented a utopian vision of freedom from centralized control. Perhaps most significantly, crypto offered a sense of meaning in an increasingly abstract world, making the clear signs of scams harder to notice.
The technology itself had failed to solve any real-world problems at scale. By 2024, the once-mighty crypto ecosystem had become a cautionary tale. Venture firms quietly scrubbed blockchain references from their websites while founders pivoted to AI and large language models.
Most reading this are likely fellow bitcoiners and nostr users who understand that Bitcoin is blockchain's only valid use case. But I shared that painful history because I believe the AI-hype cycle will follow the same trajectory.
Just like with blockchain, we're now seeing VCs who once couldn't stop talking about "Web3" falling over themselves to fund anything with "AI" in the pitch deck. The buzzwords have simply changed from "decentralized" to "intelligent."
"Vibe coding" is the perfect example – a trendy name for what is essentially just fuzzy instructions to LLMs. Developers who've spent years honing programming skills are now supposed to believe that "vibing" with an AI is somehow a legitimate methodology.
This might be controversial to some, but obvious to others:
Formal, context-free grammar will always remain essential for building precise systems, regardless of how advanced natural language technology becomes
The mathematical precision of programming languages provides a foundation that human language's ambiguity can never replace. Programming requires precision – languages, compilers, and processors operate on explicit instructions, not vibes. What "vibe coding" advocates miss is that beneath every AI-generated snippet lies the same deterministic rules that have always governed computation.
LLMs don't understand code in any meaningful sense—they've just ingested enormous datasets of human-written code and can predict patterns. When they "work," it's because they've seen similar patterns before, not because they comprehend the underlying logic.
This creates a dangerous dependency. Junior developers "vibing" with LLMs might get working code without understanding the fundamental principles. When something breaks in production, they'll lack the knowledge to fix it.
Even experienced developers can find themselves in treacherous territory when relying too heavily on LLM-generated code. What starts as a productivity boost can transform into a dependency crutch.
The real danger isn't just technical limitations, but the false confidence it instills. Developers begin to believe they understand systems they've merely instructed an AI to generate – fundamentally different from understanding code you've written yourself.
We're already seeing the warning signs: projects cobbled together with LLM-generated code that work initially but become maintenance nightmares when requirements change or edge cases emerge.
The venture capital money is flowing exactly as it did with blockchain. Anthropic raised billions, OpenAI is valued astronomically despite minimal revenue, and countless others are competing to build ever-larger models with vague promises. Every startup now claims to be "AI-powered" regardless of whether it makes sense.
Don't get me wrong—there's genuine innovation happening in AI research. But "vibe coding" isn't it. It's a marketing term designed to make fuzzy prompting sound revolutionary.
Cursor perfectly embodies this AI hype cycle. It's an AI-enhanced code editor built on VS Code that promises to revolutionize programming by letting you "chat with your codebase." Just like blockchain startups promised to "revolutionize" industries, Cursor promises to transform development by adding LLM capabilities.
Yes, Cursor can be genuinely helpful. It can explain unfamiliar code, suggest completions, and help debug simple issues. After trying it for just an hour, I found the autocomplete to be MAGICAL for simple refactoring and basic functionality.
But the marketing goes far beyond reality. The suggestion that you can simply describe what you want and get production-ready code is dangerously misleading. What you get are approximations with:
- Security vulnerabilities the model doesn't understand
- Edge cases it hasn't considered
- Performance implications it can't reason about
- Dependency conflicts it has no way to foresee
The most concerning aspect is how such tools are marketed to beginners as shortcuts around learning fundamentals. "Why spend years learning to code when you can just tell AI what you want?" This is reminiscent of how crypto was sold as a get-rich-quick scheme requiring no actual understanding.
When you "vibe code" with an AI, you're not eliminating complexity—you're outsourcing understanding to a black box. This creates developers who can prompt but not program, who can generate but not comprehend.
The real utility of LLMs in development is in augmenting existing workflows:
- Explaining unfamiliar codebases
- Generating boilerplate for well-understood patterns
- Suggesting implementations that a developer evaluates critically
- Assisting with documentation and testing
These uses involve the model as a subordinate assistant to a knowledgeable developer, not as a replacement for expertise. This is where the technology adds value—as a sophisticated tool in skilled hands.
Cursor is just a better hammer, not a replacement for understanding what you're building. The actual value emerges when used by developers who understand what happens beneath the abstractions. They can recognize when AI suggestions make sense and when they don't because they have the fundamental knowledge to evaluate output critically.
This is precisely where the "vibe coding" narrative falls apart.
-
 @ ffbcb706:b0574044
2025-05-06 09:29:41
@ ffbcb706:b0574044
2025-05-06 09:29:41Markdown test italic bold in openletter Nostr https://openletter.earth/ Have a great day
-
 @ dc0173e0:5499dd3b
2025-05-06 03:33:23
@ dc0173e0:5499dd3b
2025-05-06 03:33:23Texas’s
-
 @ e39bf33e:82567570
2025-05-06 03:22:29
@ e39bf33e:82567570
2025-05-06 03:22:2913WIN là một nền tảng giải trí trực tuyến nổi bật, mang đến cho người dùng những trải nghiệm tuyệt vời nhờ vào giao diện dễ sử dụng và tốc độ hoạt động mượt mà. Được thiết kế để đáp ứng nhu cầu giải trí của nhiều đối tượng người dùng, 13WIN không chỉ cung cấp các dịch vụ cơ bản mà còn tích hợp nhiều tính năng vượt trội, giúp người dùng có thể tận hưởng một cách tối đa các dịch vụ giải trí trên nền tảng. Giao diện của 13WIN được tối ưu hóa để mang lại sự thân thiện và dễ dàng trong việc tìm kiếm và sử dụng các tính năng. Người dùng có thể dễ dàng truy cập vào các dịch vụ giải trí yêu thích chỉ với vài cú nhấp chuột. Với sự cải tiến liên tục, 13WIN luôn tìm cách nâng cao trải nghiệm của người dùng, cập nhật các tính năng mới và tối ưu hóa mọi quy trình để người dùng có thể trải nghiệm dịch vụ một cách hoàn hảo. Dù bạn là người mới hay đã quen thuộc với nền tảng, bạn vẫn có thể dễ dàng làm quen và tận hưởng dịch vụ của 13WIN một cách nhanh chóng và hiệu quả.
Điều đáng chú ý ở 13WIN chính là hệ thống bảo mật được đầu tư mạnh mẽ, giúp người dùng yên tâm tuyệt đối khi sử dụng nền tảng này. 13WIN sử dụng công nghệ mã hóa SSL 128-bit, một trong những phương pháp bảo mật tiên tiến nhất hiện nay, giúp bảo vệ mọi thông tin cá nhân và các giao dịch của người dùng. Tất cả các giao dịch và dữ liệu của người dùng đều được mã hóa và bảo vệ an toàn tuyệt đối, tránh khỏi sự xâm nhập của các bên không mong muốn. Bên cạnh đó, 13WIN còn triển khai các biện pháp bảo vệ bổ sung như xác thực hai yếu tố (2FA), giúp nâng cao thêm mức độ bảo mật và an toàn cho tài khoản người dùng. Những biện pháp bảo mật này giúp người dùng cảm thấy hoàn toàn yên tâm khi sử dụng dịch vụ trên nền tảng, bảo vệ thông tin cá nhân và tài khoản của người dùng khỏi các nguy cơ xâm nhập hay lừa đảo. Chính sự cam kết về bảo mật và sự bảo vệ tối đa quyền lợi người dùng đã giúp 13WIN xây dựng được lòng tin từ phía người sử dụng và trở thành lựa chọn hàng đầu của nhiều người.
Bên cạnh sự chú trọng đến bảo mật, dịch vụ khách hàng của 13WIN cũng là một yếu tố quan trọng giúp nền tảng này chiếm được sự yêu mến của người dùng. Đội ngũ chăm sóc khách hàng của 13WIN luôn sẵn sàng hỗ trợ 24/7, đảm bảo rằng mọi thắc mắc và yêu cầu của người dùng sẽ được giải quyết nhanh chóng và hiệu quả. Dù là vấn đề về tài khoản hay các câu hỏi liên quan đến tính năng của nền tảng, người dùng đều có thể dễ dàng liên hệ và nhận sự hỗ trợ tận tình từ đội ngũ nhân viên chuyên nghiệp của 13WIN. Điều này không chỉ giúp người dùng cảm thấy yên tâm hơn khi tham gia mà còn nâng cao trải nghiệm sử dụng dịch vụ. Bên cạnh đó, 13WIN cũng thường xuyên tổ chức các chương trình khuyến mãi hấp dẫn, tạo cơ hội cho người dùng nhận các phần quà đặc biệt và các ưu đãi thú vị. Các chương trình này được thiết kế linh hoạt và đáp ứng nhu cầu của từng đối tượng người dùng, từ những người mới bắt đầu cho đến những khách hàng trung thành. Với tất cả những ưu điểm này, 13WIN không chỉ là một nền tảng giải trí trực tuyến mà còn là một địa chỉ đáng tin cậy cho những ai đang tìm kiếm một dịch vụ chất lượng và an toàn.
-
 @ 0fa80bd3:ea7325de
2025-04-09 21:19:39
@ 0fa80bd3:ea7325de
2025-04-09 21:19:39DAOs promised decentralization. They offered a system where every member could influence a project's direction, where money and power were transparently distributed, and decisions were made through voting. All of it recorded immutably on the blockchain, free from middlemen.
But something didn’t work out. In practice, most DAOs haven’t evolved into living, self-organizing organisms. They became something else: clubs where participation is unevenly distributed. Leaders remained - only now without formal titles. They hold influence through control over communications, task framing, and community dynamics. Centralization still exists, just wrapped in a new package.
But there's a second, less obvious problem. Crowds can’t create strategy. In DAOs, people vote for what "feels right to the majority." But strategy isn’t about what feels good - it’s about what’s necessary. Difficult, unpopular, yet forward-looking decisions often fail when put to a vote. A founder’s vision is a risk. But in healthy teams, it’s that risk that drives progress. In DAOs, risk is almost always diluted until it becomes something safe and vague.
Instead of empowering leaders, DAOs often neutralize them. This is why many DAOs resemble consensus machines. Everyone talks, debates, and participates, but very little actually gets done. One person says, “Let’s jump,” and five others respond, “Let’s discuss that first.” This dynamic might work for open forums, but not for action.
Decentralization works when there’s trust and delegation, not just voting. Until DAOs develop effective systems for assigning roles, taking ownership, and acting with flexibility, they will keep losing ground to old-fashioned startups led by charismatic founders with a clear vision.
We’ve seen this in many real-world cases. Take MakerDAO, one of the most mature and technically sophisticated DAOs. Its governance token (MKR) holders vote on everything from interest rates to protocol upgrades. While this has allowed for transparency and community involvement, the process is often slow and bureaucratic. Complex proposals stall. Strategic pivots become hard to implement. And in 2023, a controversial proposal to allocate billions to real-world assets passed only narrowly, after months of infighting - highlighting how vision and execution can get stuck in the mud of distributed governance.
On the other hand, Uniswap DAO, responsible for the largest decentralized exchange, raised governance participation only after launching a delegation system where token holders could choose trusted representatives. Still, much of the activity is limited to a small group of active contributors. The vast majority of token holders remain passive. This raises the question: is it really community-led, or just a formalized power structure with lower transparency?
Then there’s ConstitutionDAO, an experiment that went viral. It raised over $40 million in days to try and buy a copy of the U.S. Constitution. But despite the hype, the DAO failed to win the auction. Afterwards, it struggled with refund logistics, communication breakdowns, and confusion over governance. It was a perfect example of collective enthusiasm without infrastructure or planning - proof that a DAO can raise capital fast but still lack cohesion.
Not all efforts have failed. Projects like Gitcoin DAO have made progress by incentivizing small, individual contributions. Their quadratic funding mechanism rewards projects based on the number of contributors, not just the size of donations, helping to elevate grassroots initiatives. But even here, long-term strategy often falls back on a core group of organizers rather than broad community consensus.
The pattern is clear: when the stakes are low or the tasks are modular, DAOs can coordinate well. But when bold moves are needed—when someone has to take responsibility and act under uncertainty DAOs often freeze. In the name of consensus, they lose momentum.
That’s why the organization of the future can’t rely purely on decentralization. It must encourage individual initiative and the ability to take calculated risks. People need to see their contribution not just as a vote, but as a role with clear actions and expected outcomes. When the situation demands, they should be empowered to act first and present the results to the community afterwards allowing for both autonomy and accountability. That’s not a flaw in the system. It’s how real progress happens.
-
 @ c631e267:c2b78d3e
2025-03-21 19:41:50
@ c631e267:c2b78d3e
2025-03-21 19:41:50Wir werden nicht zulassen, dass technisch manches möglich ist, \ aber der Staat es nicht nutzt. \ Angela Merkel
Die Modalverben zu erklären, ist im Deutschunterricht manchmal nicht ganz einfach. Nicht alle Fremdsprachen unterscheiden zum Beispiel bei der Frage nach einer Möglichkeit gleichermaßen zwischen «können» im Sinne von «die Gelegenheit, Kenntnis oder Fähigkeit haben» und «dürfen» als «die Erlaubnis oder Berechtigung haben». Das spanische Wort «poder» etwa steht für beides.
Ebenso ist vielen Schülern auf den ersten Blick nicht recht klar, dass das logische Gegenteil von «müssen» nicht unbedingt «nicht müssen» ist, sondern vielmehr «nicht dürfen». An den Verkehrsschildern lässt sich so etwas meistens recht gut erklären: Manchmal muss man abbiegen, aber manchmal darf man eben nicht.

Dieses Beispiel soll ein wenig die Verwirrungstaktik veranschaulichen, die in der Politik gerne verwendet wird, um unpopuläre oder restriktive Maßnahmen Stück für Stück einzuführen. Zuerst ist etwas einfach innovativ und bringt viele Vorteile. Vor allem ist es freiwillig, jeder kann selber entscheiden, niemand muss mitmachen. Später kann man zunehmend weniger Alternativen wählen, weil sie verschwinden, und irgendwann verwandelt sich alles andere in «nicht dürfen» – die Maßnahme ist obligatorisch.
Um die Durchsetzung derartiger Initiativen strategisch zu unterstützen und nett zu verpacken, gibt es Lobbyisten, gerne auch NGOs genannt. Dass das «NG» am Anfang dieser Abkürzung übersetzt «Nicht-Regierungs-» bedeutet, ist ein Anachronismus. Das war vielleicht früher einmal so, heute ist eher das Gegenteil gemeint.
In unserer modernen Zeit wird enorm viel Lobbyarbeit für die Digitalisierung praktisch sämtlicher Lebensbereiche aufgewendet. Was das auf dem Sektor der Mobilität bedeuten kann, haben wir diese Woche anhand aktueller Entwicklungen in Spanien beleuchtet. Begründet teilweise mit Vorgaben der Europäischen Union arbeitet man dort fleißig an einer «neuen Mobilität», basierend auf «intelligenter» technologischer Infrastruktur. Derartige Anwandlungen wurden auch schon als «Technofeudalismus» angeprangert.
Nationale Zugangspunkte für Mobilitätsdaten im Sinne der EU gibt es nicht nur in allen Mitgliedsländern, sondern auch in der Schweiz und in Großbritannien. Das Vereinigte Königreich beteiligt sich darüber hinaus an anderen EU-Projekten für digitale Überwachungs- und Kontrollmaßnahmen, wie dem biometrischen Identifizierungssystem für «nachhaltigen Verkehr und Tourismus».
Natürlich marschiert auch Deutschland stracks und euphorisch in Richtung digitaler Zukunft. Ohne vernetzte Mobilität und einen «verlässlichen Zugang zu Daten, einschließlich Echtzeitdaten» komme man in der Verkehrsplanung und -steuerung nicht aus, erklärt die Regierung. Der Interessenverband der IT-Dienstleister Bitkom will «die digitale Transformation der deutschen Wirtschaft und Verwaltung vorantreiben». Dazu bewirbt er unter anderem die Konzepte Smart City, Smart Region und Smart Country und behauptet, deutsche Großstädte «setzen bei Mobilität voll auf Digitalisierung».
Es steht zu befürchten, dass das umfassende Sammeln, Verarbeiten und Vernetzen von Daten, das angeblich die Menschen unterstützen soll (und theoretisch ja auch könnte), eher dazu benutzt wird, sie zu kontrollieren und zu manipulieren. Je elektrischer und digitaler unsere Umgebung wird, desto größer sind diese Möglichkeiten. Im Ergebnis könnten solche Prozesse den Bürger nicht nur einschränken oder überflüssig machen, sondern in mancherlei Hinsicht regelrecht abschalten. Eine gesunde Skepsis ist also geboten.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Er ist zuerst auf Transition News erschienen.
-
 @ 502ab02a:a2860397
2025-05-06 01:06:54
@ 502ab02a:a2860397
2025-05-06 01:06:54เมื่อวานนี้เรารู้เรื่อง Meat Free Monday ของท่านเซอร์พอลกันแล้ว วันนี้เรามาต่อเนื่องกับแสงสีกันอีกนิดครับ
Anne Hathaway กับ The EVERY Company จากเจ้าหญิง The Princess Diaries สู่ราชินีโปรตีนไร้ไก่ ในยุคที่ความเปลี่ยนแปลงไม่เคาะประตู แต่มาถีบประตูบ้านเข้าใส่เลย บรรดาเซเล็บฮอลลีวูดก็ไม่ได้อยู่เฉยๆ แค่ใส่กระโปรงขึ้นพรมแดงหรือไปเล่นหนังรางวัลเท่านั้น แต่บางคน เช่น Anne Hathaway ก้าวเข้ามาอยู่เบื้องหลังระบบอาหารโลกในรูปแบบที่เงียบ…แต่เขย่าพื้นโลกได้เหมือนกัน
ใช่จ้ะ... Anne Hathaway คนเดียวกับที่เฮียเคยเห็นใน The Devil Wears Prada หรือเจ้าหญิง Mia ใน Princess Diaries ได้ลงทุนแบบเอาจริงกับบริษัทเทคโนโลยีอาหารสุดล้ำที่ชื่อว่า The EVERY Company ซึ่งพัฒนาโปรตีนจากไข่ที่ไม่ใช้ไก่ ไม่ต้องมีฟาร์ม ไม่ต้องฟัก และไม่ต้องฟูมฟักศีลธรรมให้สั่นไหวด้วยการฆ่าสัตว์เลยแม้แต่นิดเดียว
ทบทวนกันจากสัปดาห์ที่แล้วครับ The EVERY Company เดิมชื่อ Clara Foods ก่อตั้งในกลางยุค 2010s ณ ใจกลางซิลิคอนวัลเลย์ แหล่งรวมจินตนาการและเงิน VC ที่ไม่รู้จะเอาไปลงกับอะไรดี บริษัทนี้ไม่ได้เลี้ยงไก่ ไม่ได้ใช้ถาดไข่ แต่ใช้ “Precision Fermentation” ซึ่งก็คือการเอา DNA ที่เป็นรหัสของไข่ขาว (Ovalbumin) ไปใส่ในจุลินทรีย์สายพันธุ์เฉพาะ แล้วเลี้ยงด้วยน้ำตาลในถังหมัก สุดท้ายมันก็ผลิตโปรตีนออกมาที่มีโครงสร้าง “เหมือนของจริงเป๊ะ”
มันคือการทำไข่จาก “ยีสต์” ไม่ใช่จาก “แม่ไก่”
การลงทุนของ Anne ครั้งนี้ ถือเป็น B2B investment ครั้งแรกในชีวิต และดูจะไม่ใช่แค่ลงทุนแบบเซ็นเช็คเฉยๆ แล้วไปจิบไวน์ที่คานส์นะ เพราะเธอให้สัมภาษณ์ว่า
“It’s clear that our food system needs a change. EVERY is one part of a beautiful future.” (มันชัดเจนว่าระบบอาหารเราต้องเปลี่ยนแปลง EVERY คือส่วนหนึ่งของอนาคตที่งดงามนั้น)
แม้ไม่มีการเปิดเผยจำนวนเงินหรือสัดส่วนหุ้นอย่างเป็นทางการ แต่สื่ออุตสาหกรรมอาหารอย่าง Food Navigator USA ก็ชี้ว่า เธอเป็นอีกแรงที่ช่วยดันชื่อเสียงของบริษัทให้ “กลายเป็นไวรัล” ในหมู่นักลงทุน และอาจเปิดประตูสู่การยอมรับของตลาดผู้บริโภคได้ในวงกว้าง
The EVERY Company ไม่ได้หวังจะแค่ขาย “ไข่” ในซูเปอร์มาร์เก็ตแบบธรรมดาๆ แต่เริ่ม “แทรกซึม” จากเบื้องหลังในอุตสาหกรรมอาหารอย่างแยบยล จะเปลี่ยนระบบอาหารโดยใช้แนวทาง “B2B only” คือผลิตขายให้เชฟ ร้านอาหาร และโรงงานเท่านั้น (ยังไม่วางจำหน่ายปลีกทั่วไป เพราะบางตัวอย่าง EVERY Egg ยังรอรับรอง GRAS จาก FDA)
เคยมีการร่วมงานกับเชฟมิชลิน Dominique Crenn จากร้าน Atelier Crenn ในนครซานฟรานซิสโก ซึ่งเธอยืนยันว่า EVERY Egg เป็นตัวเปลี่ยนเกม ที่ทำให้เธอสามารถสร้างเมนูใหม่ที่ “ไร้สัตว์” ได้โดยไม่เสียความสร้างสรรค์หรือรสชาติ
แม้ Anne จะไม่มีตำแหน่งในบอร์ดบริหาร แต่การที่เธอลงทุนใน The EVERY Company ทำให้หลายองค์กรจับตามอง และส่งผลต่อภาพลักษณ์ของ “โปรตีนสังเคราะห์จากจุลินทรีย์” ให้ดูหรู ดูสะอาด และเหมาะกับสายสุขภาพ-มังสวิรัติ ทั้งที่จริงๆ แล้ว มันคือ “ผลิตภัณฑ์โรงงานที่ผ่านกระบวนการขั้นสูงมาก”
The EVERY Company ยังได้รับเงินลงทุนจากกลุ่มใหญ่อย่าง Temasek (กองทุนจากสิงคโปร์) และ Prosperity7 Ventures ที่เป็นแขนของ Saudi Aramco ซึ่งก็เป็นอีกประเด็นน่าคิด…ว่าพลังทุนที่อยู่เบื้องหลัง “ไข่ไม่ใช้ไก่” นี้ มาจากหลายทิศหลายทาง ทั้ง Silicon Valley, ตะวันออกกลาง และ Hollywood
การที่ Anne Hathaway ลงทุนใน EVERY ไม่ใช่เรื่องผิด แต่เป็นหมุดหมายที่น่าสนใจในยุคที่ “อาหาร” ไม่ใช่แค่เรื่องอิ่มท้อง แต่กลายเป็นการเมือง วิทยาศาสตร์ เศรษฐกิจ และการสร้างภาพลักษณ์ของคนดังในคราวเดียวกัน
ไข่ที่ไม่มีไก่ โปรตีนที่ไม่มีฟาร์ม…ดูเหมือนจะสวยงาม แต่ถ้าเรามองให้ลึก บางครั้งอาหารก็อาจไม่ใช่เรื่อง “ของกิน” อย่างเดียวอีกต่อไป
เรื่องบางเรื่อง คนในบางสังคม คนในบางกลุ่มเท่านั้น ที่จะมีโอกาสเลือกก่อน กี่ครั้งต่อกี่ครั้ง ก็แบบนี้ครับ #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 90c656ff:9383fd4e
2025-05-05 18:37:40
@ 90c656ff:9383fd4e
2025-05-05 18:37:40Bitcoin has emerged as a new economic tool in developing economies. These nations often face challenges such as high inflation, fragile banking systems, and limited access to financial services. With its unique characteristics—decentralization, censorship resistance, and limited supply—Bitcoin offers an alternative solution to protect wealth, facilitate international transactions, and promote financial inclusion.
Challenges Faced by Emerging Economies
- Inflation and Currency Devaluation
01 - Many developing countries struggle with unstable monetary policies, leading to the devaluation of their national currencies. 02 - Inflation erodes purchasing power, making it difficult for people to preserve wealth or plan long-term finances.
- Limited Access to the Banking System
01 - In many areas—especially rural regions - a significant portion of the population lacks access to banks or basic financial services. 02 - This restricts the ability to store money safely, obtain credit, and carry out secure transactions.
- Expensive Remittances and International Transactions
01 - Many citizens of developing economies rely on remittances from family members working abroad. 02 - Fees charged by financial intermediaries can be high, reducing the value received by families.
How Bitcoin Benefits Emerging Economies
- Protection Against Inflation
With its supply capped at 21 million units, Bitcoin acts as a deflationary asset, helping individuals shield their wealth from local currency devaluation. In countries like Venezuela and Argentina, where inflation is rampant, Bitcoin is used as a store of value.
- Financial Inclusion
Bitcoin removes the need for financial intermediaries, enabling anyone with internet access to participate in the global economy. Unbanked individuals can use digital wallets to store and transfer value, promoting widespread financial inclusion.
- Simplified International Transactions
Bitcoin enables fast, low-cost value transfers across borders, without relying on banks or remittance companies. This helps workers send money home, ensuring more of their earnings reach their families.
- Censorship Resistance and Government Control
In developing economies with authoritarian regimes or political instability, Bitcoin allows citizens to maintain control over their money without fear of confiscation or unfair restrictions. Its decentralized network prevents any single authority from controlling or manipulating the system.
Real Use Cases in Emerging Economies
- El Salvador
In 2021, El Salvador became the first country to adopt Bitcoin as legal tender. The goal was to reduce remittance costs and increase financial inclusion. The initiative also attracted Bitcoin-related investment and tourism, though it has faced criticism and implementation challenges.
- Nigeria
Bitcoin use in Nigeria surged due to inflation and government restrictions on financial transactions. Young entrepreneurs and freelancers use Bitcoin to receive international payments and bypass local banking limitations.
- Venezuela
Amid economic crisis and hyperinflation, Bitcoin became a key tool for protecting wealth and conducting transactions. Many Venezuelan families rely on Bitcoin to purchase essential goods and send or receive money from abroad.
Challenges of Using Bitcoin in Emerging Markets
- Volatility
Bitcoin's high price volatility can make it risky for people relying on it as a store of value. This instability may discourage its use for daily transactions.
- Limited Infrastructure
Bitcoin usage requires internet access and digital devices, which may be lacking in areas with underdeveloped infrastructure.
- Education and Adaptation
Adopting Bitcoin requires a certain level of technical knowledge, and the lack of financial literacy can hinder large-scale adoption. Many people still prefer traditional currencies due to unfamiliarity or distrust of Bitcoin.
The Future of Bitcoin in Emerging Economies
- Infrastructure Development
Projects promoting internet access and digital tools can significantly boost Bitcoin adoption in these regions.
- Stability and Trust
As the market matures, Bitcoin's volatility may decrease, making it more practical as a medium of exchange and store of value.
- Education and Empowerment
Financial education initiatives can help people understand and harness the benefits of Bitcoin, easing its integration into daily life.
In summary, Bitcoin has a transformative role in emerging economies, offering a strong alternative to traditional financial systems. Its ability to hedge against inflation, promote financial inclusion, and facilitate international transactions makes it a crucial tool for millions of people.
While challenges like volatility and infrastructure gaps remain, Bitcoin’s potential to empower individuals in developing nations is clear. As a decentralized digital asset, it represents not only a technological innovation but also a hope for a fairer and more accessible economic future.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ e83b66a8:b0526c2b
2025-05-06 09:17:39
@ e83b66a8:b0526c2b
2025-05-06 09:17:39I’m going to talk about Ethereum, hear me out.
Ethereum is a Turing complete consensus blockchain tokenised by its own currency Ether.
This idea by Vitalik Buterin was incredibly compelling and still is today, even though few real world use cases have emerged.
For example, as a company, I could pay a carbon tax in Ether, locked into a smart contract. If the temperate rises by more than “n” degrees year on year based on a known agreed external (blind) oracle, say a weather station located near my factory.
Fantastic, we now have an automatic climate tax.
In reality, few realistic applications exist, however the idea is very compelling and many flocked to Ethereum as a promise of the future. This inflated its utility token “Ether” into stratospherically high prices.
This, in turn, attracted speculative investors and traders only looking at the price signal of the token and no longer considering the utility. This created a bubble which has gradually deflated over time.
This is why we are seeing Bitcoin, which only attempts to be money, succeed relative to Ethereum.
As Ethereum fails, and Bitcoin development strides on, an opportunity arises to try to do what Ethereum and all the other related altcoins have so far failed to do. Computational utility. And to do this on Bitcoin, the most successful “Crypto”.
The first unintended hijack of Ethereums utility are the JPEGs we are seeing on our blockchain.
This latest drive to make Bitcoin Turing complete is potentially the final destination for developers keen to explore the potential of Bitcoins eco-system.
Perhaps Bitcoin is going to absorb all the altcoins. Perhaps that is the goal of Bitcoins developers.
I don’t comment whether this is good or bad, I’m just exploring whether this may be the agenda.
-
 @ 39cc53c9:27168656
2025-04-09 07:59:35
@ 39cc53c9:27168656
2025-04-09 07:59:35The new website is finally live! I put in a lot of hard work over the past months on it. I'm proud to say that it's out now and it looks pretty cool, at least to me!
Why rewrite it all?
The old kycnot.me site was built using Python with Flask about two years ago. Since then, I've gained a lot more experience with Golang and coding in general. Trying to update that old codebase, which had a lot of design flaws, would have been a bad idea. It would have been like building on an unstable foundation.
That's why I made the decision to rewrite the entire application. Initially, I chose to use SvelteKit with JavaScript. I did manage to create a stable site that looked similar to the new one, but it required Jav aScript to work. As I kept coding, I started feeling like I was repeating "the Python mistake". I was writing the app in a language I wasn't very familiar with (just like when I was learning Python at that mom ent), and I wasn't happy with the code. It felt like spaghetti code all the time.
So, I made a complete U-turn and started over, this time using Golang. While I'm not as proficient in Golang as I am in Python now, I find it to be a very enjoyable language to code with. Most aof my recent pr ojects have been written in Golang, and I'm getting the hang of it. I tried to make the best decisions I could and structure the code as well as possible. Of course, there's still room for improvement, which I'll address in future updates.
Now I have a more maintainable website that can scale much better. It uses a real database instead of a JSON file like the old site, and I can add many more features. Since I chose to go with Golang, I mad e the "tradeoff" of not using JavaScript at all, so all the rendering load falls on the server. But I believe it's a tradeoff that's worth it.
What's new
- UI/UX - I've designed a new logo and color palette for kycnot.me. I think it looks pretty cool and cypherpunk. I am not a graphic designer, but I think I did a decent work and I put a lot of thinking on it to make it pleasant!
- Point system - The new point system provides more detailed information about the listings, and can be expanded to cover additional features across all services. Anyone can request a new point!
- ToS Scrapper: I've implemented a powerful automated terms-of-service scrapper that collects all the ToS pages from the listings. It saves you from the hassle of reading the ToS by listing the lines that are suspiciously related to KYC/AML practices. This is still in development and it will improve for sure, but it works pretty fine right now!
- Search bar - The new search bar allows you to easily filter services. It performs a full-text search on the Title, Description, Category, and Tags of all the services. Looking for VPN services? Just search for "vpn"!
- Transparency - To be more transparent, all discussions about services now take place publicly on GitLab. I won't be answering any e-mails (an auto-reply will prompt to write to the corresponding Gitlab issue). This ensures that all service-related matters are publicly accessible and recorded. Additionally, there's a real-time audits page that displays database changes.
- Listing Requests - I have upgraded the request system. The new form allows you to directly request services or points without any extra steps. In the future, I plan to enable requests for specific changes to parts of the website.
- Lightweight and fast - The new site is lighter and faster than its predecessor!
- Tor and I2P - At last! kycnot.me is now officially on Tor and I2P!
How?
This rewrite has been a labor of love, in the end, I've been working on this for more than 3 months now. I don't have a team, so I work by myself on my free time, but I find great joy in helping people on their private journey with cryptocurrencies. Making it easier for individuals to use cryptocurrencies without KYC is a goal I am proud of!
If you appreciate my work, you can support me through the methods listed here. Alternatively, feel free to send me an email with a kind message!
Technical details
All the code is written in Golang, the website makes use of the chi router for the routing part. I also make use of BigCache for caching database requests. There is 0 JavaScript, so all the rendering load falls on the server, this means it needed to be efficient enough to not drawn with a few users since the old site was reporting about 2M requests per month on average (note that this are not unique users).
The database is running with mariadb, using gorm as the ORM. This is more than enough for this project. I started working with an
sqlitedatabase, but I ended up migrating to mariadb since it works better with JSON.The scraper is using chromedp combined with a series of keywords, regex and other logic. It runs every 24h and scraps all the services. You can find the scraper code here.
The frontend is written using Golang Templates for the HTML, and TailwindCSS plus DaisyUI for the CSS classes framework. I also use some plain CSS, but it's minimal.
The requests forms is the only part of the project that requires JavaScript to be enabled. It is needed for parsing some from fields that are a bit complex and for the "captcha", which is a simple Proof of Work that runs on your browser, destinated to avoid spam. For this, I use mCaptcha.
-
 @ ba36d0f7:cd802cba
2025-04-06 16:43:05
@ ba36d0f7:cd802cba
2025-04-06 16:43:051. Reglas Esenciales
✔ Pieza Tocada, Pieza Movida: Si tocas una pieza, debes moverla (si es legal).
✔ Aviso de Jaque: Decir "jaque" al atacar al rey (opcional en torneos oficiales).
✔ Jaque Mate Termina: El juego acaba inmediatamente — no hay que capturar al rey.
✔ Oferta de Tablas: Puedes ofrecer tablas después de tu movimiento, antes de pulsar el reloj.
2. Etiqueta en Torneos
-
Saludo: Apretón de manos antes y después de la partida.
-
Silencio: No hablar durante el juego (excepto "jaque" o "¿tablas?").
-
Reloj: Presiónalo con la misma mano que movió.
-
Rendición: Voltea tu rey o di "me rindo" (no solo te vayas).
Errores Comunes
❌ Hacer ruido con las piezas para distraer.
❌ Mirar fijamente el tablero del rival.
❌ Hacer jugadas falsas para probar su atención.
3. Modales en Ajedrez Online
-
Sin Retrasos: Deja que el tiempo se agote solo si estás perdido.
-
Cortesía: Escribe "Buen juego" ("GG") al finalizar.
-
Evita el "Berserk": No abuses de configuraciones rápidas para presionar al rival.
Faltas Graves
❌ Trampas: Usar motores de análisis, mirar otras partidas.
❌ Spammear mensajes o emojis.
❌ Abandonar sin rendirse formalmente.
-
-
 @ 90c656ff:9383fd4e
2025-05-05 17:07:59
@ 90c656ff:9383fd4e
2025-05-05 17:07:59Regulations play a fundamental role in the evolution of the global financial market, laying the foundation for stability, security, and trust in economic transactions. However, in an increasingly globalized and digital world, regulatory challenges have become more complex—especially with the emergence of disruptive financial innovations such as Bitcoin and decentralized finance (DeFi). The interaction between regulation and the financial market has deep consequences, both positive and negative, shaping the future of the global economy.
The Importance of Regulations in the Financial Market:
01 - Economic Stability: Financial laws and regulations help prevent risky practices such as irresponsible lending and excessive speculation. 02 - Consumer Protection: Regulations ensure that consumers and investors have access to clear and accurate information, preventing fraud and abuse. 03 - Anti-Money Laundering and Counter-Terrorism: Policies such as Know Your Customer (KYC) and Anti-Money Laundering (AML) ensure that illicit funds do not enter the financial system.
Regulatory Challenges in a Globalized Market:
01 - Market Interconnectivity: The global financial market is highly interconnected, and crises in one country can quickly spread to others. This demands more efficient international coordination among regulators. 02 - Technological Innovation: The rise of disruptive technologies like blockchain or timechain has challenged traditional regulatory models. Many governments are still trying to strike a balance between encouraging innovation and reducing risk. 03 - Compliance Costs: Financial companies face rising costs to meet increasingly strict regulations, which can impact profitability and create barriers for new entrants.
The Impact of Regulation on the Global Financial Market:
- Positive Impacts
01 - Investor Confidence: Clear rules and effective enforcement increase investor trust, promoting financial market growth. 02 - Economic Resilience: Well-designed regulations make the financial system more resistant to economic shocks. 03 - Attraction of Foreign Capital: Jurisdictions with sound regulatory governance attract investments from countries and companies seeking stability.
- Negative Impacts
01 - Excessive Bureaucracy: Overly complex regulations can hinder innovation and economic growth, especially for small businesses. 02 - Capital Flight: Companies may relocate operations to countries with looser laws, harming the economies of more regulated regions. 03 - Ineffectiveness in Global Contexts: National rules don’t always work well in global markets. Lack of international cooperation can create loopholes for bad actors.
The Role of International Institutions:
01 - Global Standards: Organizations work to create international standards, such as the Basel Accords for minimum capital requirements for banks. 02 - Crisis Resolution: International institutions also act as mediators and providers of financial assistance during global crises, as seen during the 2020–2021 pandemic.
Regulation and Innovation: A Necessary Balance
01 - Encouraging Innovation: Regulators should allow emerging technologies to grow, enabling solutions like blockchain or timechain to develop freely. 02 - Risks of No Regulation: Without proper rules, innovative markets may attract fraudulent behavior, undermining public trust.
In summary, regulations are essential to maintaining the integrity and stability of the global financial market. They protect participants, prevent crises, and foster a trustworthy environment. However, globalization and rapid technological change challenge regulators to constantly adapt.
The balance between security and innovation is vital for the future of finance. Effective rules must be flexible enough to keep up with change and strong enough to protect participants. In this way, the global financial market can continue to evolve, promoting sustainable and fair economic prosperity.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ aa8de34f:a6ffe696
2025-03-21 12:08:31
@ aa8de34f:a6ffe696
2025-03-21 12:08:3119. März 2025
🔐 1. SHA-256 is Quantum-Resistant
Bitcoin’s proof-of-work mechanism relies on SHA-256, a hashing algorithm. Even with a powerful quantum computer, SHA-256 remains secure because:
- Quantum computers excel at factoring large numbers (Shor’s Algorithm).
- However, SHA-256 is a one-way function, meaning there's no known quantum algorithm that can efficiently reverse it.
- Grover’s Algorithm (which theoretically speeds up brute force attacks) would still require 2¹²⁸ operations to break SHA-256 – far beyond practical reach.
++++++++++++++++++++++++++++++++++++++++++++++++++
🔑 2. Public Key Vulnerability – But Only If You Reuse Addresses
Bitcoin uses Elliptic Curve Digital Signature Algorithm (ECDSA) to generate keys.
- A quantum computer could use Shor’s Algorithm to break SECP256K1, the curve Bitcoin uses.
- If you never reuse addresses, it is an additional security element
- 🔑 1. Bitcoin Addresses Are NOT Public Keys
Many people assume a Bitcoin address is the public key—this is wrong.
- When you receive Bitcoin, it is sent to a hashed public key (the Bitcoin address).
- The actual public key is never exposed because it is the Bitcoin Adress who addresses the Public Key which never reveals the creation of a public key by a spend
- Bitcoin uses Pay-to-Public-Key-Hash (P2PKH) or newer methods like Pay-to-Witness-Public-Key-Hash (P2WPKH), which add extra layers of security.
🕵️♂️ 2.1 The Public Key Never Appears
- When you send Bitcoin, your wallet creates a digital signature.
- This signature uses the private key to prove ownership.
- The Bitcoin address is revealed and creates the Public Key
- The public key remains hidden inside the Bitcoin script and Merkle tree.
This means: ✔ The public key is never exposed. ✔ Quantum attackers have nothing to target, attacking a Bitcoin Address is a zero value game.
+++++++++++++++++++++++++++++++++++++++++++++++++
🔄 3. Bitcoin Can Upgrade
Even if quantum computers eventually become a real threat:
- Bitcoin developers can upgrade to quantum-safe cryptography (e.g., lattice-based cryptography or post-quantum signatures like Dilithium).
- Bitcoin’s decentralized nature ensures a network-wide soft fork or hard fork could transition to quantum-resistant keys.
++++++++++++++++++++++++++++++++++++++++++++++++++
⏳ 4. The 10-Minute Block Rule as a Security Feature
- Bitcoin’s network operates on a 10-minute block interval, meaning:Even if an attacker had immense computational power (like a quantum computer), they could only attempt an attack every 10 minutes.Unlike traditional encryption, where a hacker could continuously brute-force keys, Bitcoin’s system resets the challenge with every new block.This limits the window of opportunity for quantum attacks.
🎯 5. Quantum Attack Needs to Solve a Block in Real-Time
- A quantum attacker must solve the cryptographic puzzle (Proof of Work) in under 10 minutes.
- The problem? Any slight error changes the hash completely, meaning:If the quantum computer makes a mistake (even 0.0001% probability), the entire attack fails.Quantum decoherence (loss of qubit stability) makes error correction a massive challenge.The computational cost of recovering from an incorrect hash is still incredibly high.
⚡ 6. Network Resilience – Even if a Block Is Hacked
- Even if a quantum computer somehow solved a block instantly:The network would quickly recognize and reject invalid transactions.Other miners would continue mining under normal cryptographic rules.51% Attack? The attacker would need to consistently beat the entire Bitcoin network, which is not sustainable.
🔄 7. The Logarithmic Difficulty Adjustment Neutralizes Threats
- Bitcoin adjusts mining difficulty every 2016 blocks (\~2 weeks).
- If quantum miners appeared and suddenly started solving blocks too quickly, the difficulty would adjust upward, making attacks significantly harder.
- This self-correcting mechanism ensures that even quantum computers wouldn't easily overpower the network.
🔥 Final Verdict: Quantum Computers Are Too Slow for Bitcoin
✔ The 10-minute rule limits attack frequency – quantum computers can’t keep up.
✔ Any slight miscalculation ruins the attack, resetting all progress.
✔ Bitcoin’s difficulty adjustment would react, neutralizing quantum advantages.
Even if quantum computers reach their theoretical potential, Bitcoin’s game theory and design make it incredibly resistant. 🚀
-
 @ 5188521b:008eb518
2025-05-06 08:09:37
@ 5188521b:008eb518
2025-05-06 08:09:37Macaron returns, fluffs his white linen napkin, and takes his seat at their table, “Thank you, John, for extending my French people such great mercy as to be allowed to transact freely on the Bitcoin blockchain.” He extends his arm out towards a waiter, “Monsieur? Champagne for the three of us please!”
Vrrrm! “I can’t believe we were able to find an American Mustang in this French countryside. I am ripping down these narrow roads!” John celebrates.
“Bloody hell, slow down!” Lily begs as her oversized diamond dangle earrings sway side to side. “You’ve got nothing to prove, John. Big man in your yankee ten-gallon hat. Let’s just get there safely.”
John slows to give her a smoldering look, “Aww, my sweet British compatriot, you care about me!”
“Bollocks! I care about not dying!” Lily retorts. “Now focus on the mission. We need to save a boatload of English border collies — literally. Frenchman Macaron wants to groom them into French poodles!”
John wags a finger off the wheel to reply in his Southern drawl, “However, my sweet Lily flower, my US Hash Force intends to project power to coerce the French for the dogs’ release!”
Lily bats his finger away, “Yes, but may I remind you, my arrogant wanker, geographically challenged friend, MI6’s intel says to steadily power on any miners as His Majesty’s Hash Force may do. The border collies’ barge will take about an hour to flee France, cross the English channel, and safely reach our shores so we don’t want to burst their souffle too quickly. Oh, and the barge is armed with explosives controlled by a remote detonator. When Macaron asks for his bitcoin ransom payment in exchange for the dogs’ release, how do you cowboys plan to help from across the pond?”
John takes both hands off the wheel to flex his biceps, “Shock and awe, Lily. Full Throttle! We’re not giving the French a single sat. Instead, we’re diverting maximum energy to the U.S. Hash Force, of course!”
Lily guffaws, “And where is this sudden surge of readily available power supposed to come from undetected?”
“No need to worry my English crumpet! Our back of the envelope calculations suggest that, with a little help from the Texas of the North, there’s enough flared natural gas in the U.S. to run the entire Bitcoin network!” John proudly replies.
Lily’s jaw drops, “So miners have already stealthily built out the infrastructure to capture wasted natural gas flares for the benefit of the U.S. government, but are waiting to turn them on until commanded to by the U.S. Hash Force?!”
“Yup! As soon as Macaron sees our hash power come online, we’re going to try to start mining blocks on the Bitcoin network to Denial of Service (DOS) attack any UTXOs with a known history of French transactions.”
“A DOS attack, for peace?” Lily asks skeptically.
“Peace through strength, baby! If you don’t comply with America’s dog rights standards, you get censored. America saves British dogs again, and without a single shot fired!”
“Not fair! It’s only because our MI6 chainanalysis intel knows which Bitcoin addresses to censor on the blockchain we suspect belong to Macaron and his government that this plan even has a shot at succeeding. You’re lucky Macaron is even more self-assured than you Americans. That’s the only reason France doesn’t have a Hash Force of its own to project power back!”
John pulls the Mustang up to the front of the fancy French restaurant, Chandelier. Lily grabs her green purse that matches her elegant emerald ball gown, and they head inside to meet Macaron.
John and Lily spot Macaron sitting alone at the white linen table closest to the dance floor. He’s tapping his Louis Vuitton snake leather shoes, checking his Chanel watch, and fluffing his floofy black French Hermès beret. The red French ascot spilling out of his black and white blouse looks ridiculous.
John lets out a big sigh, and Macaron stands with open arms, “Lily, John, welcome to France!” Before John can flinch away, Macaron kisses him on both cheeks. He lifts up Lily’s hand for a kiss, “Mademoiselle.”
John raises his hand, “Waiter! I’ll take a bourbon, neat. And make it a double!” John calls out.
Slap!
“Hey, what was that for, Frenchie?” John asks as he rubs his face.
“Rude American, where are your manners?” Macaron asks as he pulls out a hidden red detonator clipped in the folds of his ascot. “Don’t drive me to prematurely push this button and blow up the boat carrying your English doggies! First, send me my bitcoin ransom payment. Then we can celebrate with drinks!” Macaron demands.
“In your dreams, Frenchie!” John presses his finger to his ear, “Uniform, Sierra, Alpha!”
Macaron turns to Lily and scoffs, “What is this rude American man doing, Lily?”
Annoyed, Lily answers, “Check your bitcoin UTXOs. Notice anything?”
Macaron frantically queries his Bitcoin node remotely from his cellphone and breathes a sigh of relief, “Phew. No, I don’t notice anything at all. All of my unspent bitcoin is still under the control of my government’s private key.”
“And it’ll stay that way, too!” John beats his chest. “You mess with the US, and you get the Hash Force! We just secretly doubled the difficulty to mine a block by turning on all of our miners — as many miners as the entire existing Bitcoin network! Now you’ll have to wait twice as long for your French bitcoin transactions to confirm! That is, unless you release the barge of dogs right now!”
Lily drops down to the table and buries her face in her palms to hide her embarrassment.
Flustered, Macaron furiously types out a long text message with the order to release the barge of English Border Collies to cross the English channel. “There, I’ve let the dogs out! Will you two please excuse me for a moment? I have to place a call with my government to confirm we haven’t lost our property rights to spend our bitcoin.
Beaming with pride, John falls back into his chair at the table. “We did it, Lily! Quick, give the command for His Majesty’s Hash Force to power on so we can 51% attack this guy!”
Lily finally stops rubbing her eyes, “John, that isn’t how any of this works!”
“What do you mean?” he asks.
“Within a 2,016 block difficulty adjustment period, doubling the hash power means the global Bitcoin network will mine new blocks twice as fast, not slower! At least, until the 2,016 block period ends and the difficulty adjusts so miners resume taking on average 10 minutes to generate a valid block. And sure, maybe the US has a political incentive to not collect the fees of any transactions of UTXOs with a known French association, but the rest of the network’s miners will happily profit from the sats you leave in the mempool! But most of all, the Bitcoin network is now just twice as secure from attack!”
John’s double bourbon finally arrives at the table. Selfishly focused on his own glass, he doesn’t bother to stop the waiter in case Lily wants to order a drink of her own. He drinks a big gulp, “But if you give the order for His Majesty’s Hash Force to power on, won’t we have over 51% of the hash power of the Bitcoin network? We can write Macaron’s bitcoin out of existence!”
Lily crosses her arms, “Not exactly. It’s not enough to just surpass half the hashrate. We also need to maintain a higher hashrate than the legacy chain to generate more chain weight to then reorg the other chain when we join the legacy network. We would have to be mining this heavier chain in secret, but in one bombastic order you just completely blew apart our whole plan! Now we’d need some sort of massive collusion somehow between existing miners, and some secret stealth miners, to have any power projection.”
John mutters under his breath, “Frenchie’s been gone a long time. Wonder what he’s up to….”
Macaron returns, fluffs his white linen napkin, and takes his seat at their table, “Thank you, John, for extending my French people such great mercy as to be allowed to transact freely on the Bitcoin blockchain.” He extends his arm out towards a waiter, “Monsieur? Champagne for the three of us please!” Macaron turns to John and Lily, “After my phone call, I am in much better spirits. Though I’m bitter you denied paying our bitcoin ransom, I’m grateful you’re furthering the security of the Bitcoin network.”
In his excitement, Macaron leans forward and claps his hands together, “You two are so lucky to be dining with me tonight. You won’t have to drink that sparkling-wine-swill you have in your home countries. Tonight, you’ll get to have proper champagne, from the Champagne region of France — my treat!”
John grunts in disgust, “Macaron, you can order champagne, but I’ve got my bourbon.”
Lily steps on John’s foot, “Ow! What was that for?” John shrieks.
“Aren’t you going to ask me if I want anything?” Lily asks.
“Huh?” John replies confusedly.
Macaron takes Lily’s hand, “Mademoiselle, in addition to champagne, can I get you anything else?”
Lily recoils her hand back, “Gin martini. Shaken, not stirred.”
“Lily, may I ask you another question?” Macaron asks sweetly.
“Bloody hell, what is it, Macaron?” she responds while rolling her eyes.
“Why do I get the feeling that forgetting to ask you what you’d like to drink isn’t the first time John has neglected to ask you what you wanted?”
Lily’s eyes light up as she leans in closer to Macaron, “Why, yes. This isn’t the first time John’s ever disregarded my needs. You know, he’s always only thinking about himself, his own ego, and he never misses a chance to interrupt me—”
“—That’s not true!” John interrupts.
Lily kicks him under the table, “See what I mean?”
Macaron whisks Lily’s hair behind her ear, “You have such beautiful earrings, Lily. Did John buy those for you?”
“No, John never buys me anything.”
“What do you mean?” John protests.
Lily shrugs him off and Macaron leans in closer to Lily to whisper just loud enough for John to hear, “You know, in my country, men like me know how to show a lady respect.”
John stands up and extends out his hand, “C’mon, Lily. I think it’s time I take you out onto the floor for a dance.”
She shakes her head, so he stomps on her feet under the table.
“Ow!” Lily shrieks.
“I insist,” John presses. “They’re playing my song, Don’t Stop Believin’. C’mon!”
On the dance floor, John pulls Lily close to whisper in her ear, “What are you doing? We’ve finished our mission. Let’s ensure the dogs safely cross the English channel and get out of here! The way you’re flirting with him we’ll never leave!”
Lily blushes, “John, are you that blind? If Macaron is suddenly being sweet to us, then he must be scheming something.”
“What’s that supposed to mean?” John shakes his head. “Look, there’s no time to argue. We can’t risk him blowing up the barge as long as he’s got that remote detonator clipped to his ascot! He’s in a jubilant mood for now, but those French can be so melodramatic. We’ve got to get the detonator to ensure the safety of the dogs until they reach safe harbor at your shores.”
John’s box step dancing pace quickens as he looks over to check on Macaron. He spots him placing an order with the waiter and grits his teeth, “He’s pure evil. He was willing to kill the English border collies if he didn’t get ransom payment for not grooming them into French poodles. Only the threat of our Hash Force forced him to comply with our demand for their release!”
Lily breaks away from John to do a twirl on the dance floor; her elegant flowy green dress tries to keep up. She flips her hair and winks at Macaron, “Maybe I should flirt with him some more? After all, he’s so handsome — and he listens to me!”
John stops dancing and stomps his feet.
“Aww, are you jealous, John?” Lily asks.
“Jealous?!”
Lily floats back to John, digs her nails into the back of his neck, and nibbles on his ear as she whispers, “John, you better dip me on this dance floor! Otherwise, I’m going to ask him to draw me like one of his French girls. C’mon John, Don’t stop believin’!”
Ahem Macaron clears his throat, adjusts his detonator-pinned ascot, and taps Lily on the shoulder.
“Mademoiselle, may I have this dance?”
“Oh, certainly,” she replies. “Better than this brute with two left feet!”
John grunts in dissatisfaction and bolts back to the table.
With Macaron distracted dancing with Lily for what feels like an eternity, John defiantly presses his finger to his ear. “MI6 — status report. What’s taking so long?” he mutters under his breath. “I hate seeing this Frenchie dance with an English lass who deserves so much better. It’s driving me crazy!”
“You just gotta distract him from detonation for ten more minutes,” a British accent replies. “Intel shows the puppy barge armed with explosives has almost reached us across the channel, and then we can safely disarm it.”
“USHF, come in,” John queries.
“We’ve got trouble! The global energy grid has spiked along the Asian seaboard, and among the French alps. Looks like a secret French Hash Force we’ve never detected is colluding with the existing Chinese, Japanese, and Tibetan miners!
They’ve stopped including American-linked bitcoin address transactions in their blocks! Can you politely get him to back down? We’ve already played our power-projection show-of-force card!”
“Ok, I’ll do my best to play nice with Frenchie, but no promises!” John cautions. As he watches Lily and Macaron dance with disdain, a waiter approaches him at the table.
“Here you are, monsieur. Your appetizer.”
“Appetizer? I didn’t order an appetizer! All I ordered was this bourbon.”
“I’m sorry monsieur, but the other gentleman of your party insists. He said he offers this delicacy as a gift. A token of appreciation for the mercy demonstrated today by you, the quote Big American Man enquote.”
John looks on the dance floor and sees Macaron give him a nod with a big wiley grin. Lily gives him the “go-ahead” signal, so John pops one of the hot slimy appetizer balls into his mouth.
“Mhmm! These are tastier than Ma’s Frito Pie!” he shouts as Macaron and Lily walk over to join him back at the table. John continues, “These remind me of the Rocky Mountain oysters we have back at home! Of course, I’m grateful they aren’t, if you know what I mean. What are they, anyways?”
“Escargot,” the Frenchman replies, “a local specialty.”
“Escar-what-now?” John asks.
“Snails!” Lily clarifies.
John gags and spits his half-eaten snail onto the floor. He stands up and slams his ten-gallon cowboy hat on the table. “Ok, that’s it! I’ve had enough! Macaron, stop playing nice. We know you’ve activated some secret alliance with the miners on the other side of the globe! What’re you up to?”
“John, don’t upset him! Think about the puppies!” Lily pleads.
“To heck with the puppies! I’m not letting this man stand up a Hash Force to DOS attack us! You hear that, Macaron? You mess with the best, and we’ll use kinetic force against your miners stashed in the caves of the French alps!” Tsk! Tsk! Tsk! Macaron wags his finger, and pulls out the detonator switch clipped to his ascot.
“Silly pompous American, did you forget I still have the detonator? Did you really think I was going to let you get away with rescuing your hideous English border collies? Life is one giant power projection game, and the way nation states survive is by mutually assured preservation. In exchange for taming the unwieldy fur of Tibetan Mastiffs, Chinese Chow Chows, and Japanese Shih-Tzu and Shiba Inus, these countries pledged their miners to our stealthy French Hash Force when we’re in need. Well, thanks to your little stunt, not only did I find the perfect opportunity to project power back at you arrogant Americans, but also dump these hideous dogs given to me onto your barge, so they’re the British Isles’ problem now!”
“But we’ll be overrun by doges!” Lily gasps in horror.
“Yes, Lily! That’s what you get for partnering with John! What do Americans say?” Macaron asks rhetorically. “That’s right, ‘No dogs left behind!’ But most of all, John, I just wanted one last dance with your girlfriend, and to watch you eat snails!” French nasally honking laughing sounds
Lily shouts back, “I’m not his girlfriend!” She pulls a whistle out of her purse and blows it as hard as she can, but it doesn’t make a sound. John looks at her confused, and Macaron honks even harder. The whole restaurant starts to rumble, and the chandeliers sway from the ceiling.
“What’s this!?” Macaron shouts.
Gradually, then suddenly a stampede of bulldogs comes barreling into the dining room, knocking over all the tables, and tackling Macaron! As he falls, the detonator gets knocked into the air, and Lily catches it just before it hits the floor.
John looks at her, bewildered, and stammers, “You…. you let the Bitcoin dogs out??”
“You think you wankers got all the tricks? The English have a few surprises too! Now c’mon, let’s flee out the back in my British Mini Cooper. And this time, I’m driving!”
Will Schoellkopf is the author of two books: Bitcoin Girl Save the World and The Bitcoin Dog: Following the Scent to the Bitcoin C++ Source Code. He hosts the Bitcoin podcast It’s So Early! and publishes a weekly newsletter, featuring his favorite Bitcoin Posts of the Week, at realbitcoindog.com. His work has appeared in the anthology 21 Futures: Tales from the Timechain, in print at Bitcoin Magazine, Citadel21, Stackchain Magazine and online at Satoshi’s Journal. Follow him on Nostr and X @realBitcoinDog, or email will@realbitcoindog.com
-
 @ 6e64b83c:94102ee8
2025-05-05 16:50:13
@ 6e64b83c:94102ee8
2025-05-05 16:50:13Nostr-static is a powerful static site generator that transforms long-form Nostr content into beautiful, standalone websites. It makes your content accessible to everyone, even those not using Nostr clients. For more information check out my previous blog post How to Create a Blog Out of Nostr Long-Form Articles
What's New in Version 0.7?
RSS and Atom Feeds
Version 0.7 brings comprehensive feed support with both RSS and Atom formats. The system automatically generates feeds for your main content, individual profiles, and tag-specific pages. These feeds are seamlessly integrated into your site's header, making them easily discoverable by feed readers and content aggregators.
This feature bridges the gap between Nostr and traditional web publishing, allowing your content to reach readers who prefer feed readers or automated content distribution systems.
Smart Content Discovery
The new tag discovery system enhances your readers' experience by automatically finding and recommending relevant articles from the Nostr network. It works by:
- Analyzing the tags in your articles
- Fetching popular articles from Nostr that share these tags
- Using configurable weights to rank these articles based on:
- Engagement metrics (reactions, reposts, replies)
- Zap statistics (amount, unique zappers, average zap size)
- Content quality signals (report penalties)
This creates a dynamic "Recommended Articles" section that helps readers discover more content they might be interested in, all while staying within the Nostr ecosystem.
See the new features yourself by visiting our demo at: https://blog.nostrize.me