-
 @ b17fccdf:b7211155
2025-03-25 11:23:36
@ b17fccdf:b7211155
2025-03-25 11:23:36Si vives en España, quizás hayas notado que no puedes acceder a ciertas páginas webs durante los fines de semana o en algunos días entre semana, entre ellas, la guía de MiniBolt.
Esto tiene una razón, por supuesto una solución, además de una conclusión. Sin entrar en demasiados detalles:
La razón
El bloqueo a Cloudflare, implementado desde hace casi dos meses por operadores de Internet (ISPs) en España (como Movistar, O2, DIGI, Pepephone, entre otros), se basa en una orden judicial emitida tras una demanda de LALIGA (Fútbol). Esta medida busca combatir la piratería en España, un problema que afecta directamente a dicha organización.
Aunque la intención original era restringir el acceso a dominios específicos que difundieran dicho contenido, Cloudflare emplea el protocolo ECH (Encrypted Client Hello), que oculta el nombre del dominio, el cual antes se transmitía en texto plano durante el proceso de establecimiento de una conexión TLS. Esta medida dificulta que las operadoras analicen el tráfico para aplicar bloqueos basados en dominios, lo que les obliga a recurrir a bloqueos más amplios por IP o rangos de IP para cumplir con la orden judicial.
Esta práctica tiene consecuencias graves, que han sido completamente ignoradas por quienes la ejecutan. Es bien sabido que una infraestructura de IP puede alojar numerosos dominios, tanto legítimos como no legítimos. La falta de un "ajuste fino" en los bloqueos provoca un perjuicio para terceros, restringiendo el acceso a muchos dominios legítimos que no tiene relación alguna con actividades ilícitas, pero que comparten las mismas IPs de Cloudflare con dominios cuestionables. Este es el caso de la web de MiniBolt y su dominio
minibolt.info, los cuales utilizan Cloudflare como proxy para aprovechar las medidas de seguridad, privacidad, optimización y servicios adicionales que la plataforma ofrece de forma gratuita.Si bien este bloqueo parece ser temporal (al menos durante la temporada 24/25 de fútbol, hasta finales de mayo), es posible que se reactive con el inicio de la nueva temporada.

La solución
Obviamente, MiniBolt no dejará de usar Cloudflare como proxy por esta razón. Por lo que a continuación se exponen algunas medidas que como usuario puedes tomar para evitar esta restricción y poder acceder:
~> Utiliza una VPN:
Existen varias soluciones de proveedores de VPN, ordenadas según su reputación en privacidad: - IVPN - Mullvad VPN - Proton VPN (gratis) - Obscura VPN (solo para macOS) - Cloudfare WARP (gratis) + permite utilizar el modo proxy local para enrutar solo la navegación, debes utilizar la opción "WARP a través de proxy local" siguiendo estos pasos: 1. Inicia Cloudflare WARP y dentro de la pequeña interfaz haz click en la rueda dentada abajo a la derecha > "Preferencias" > "Avanzado" > "Configurar el modo proxy" 2. Marca la casilla "Habilite el modo proxy en este dispositivo" 3. Elige un "Puerto de escucha de proxy" entre 0-65535. ej: 1080, haz click en "Aceptar" y cierra la ventana de preferencias 4. Accede de nuevo a Cloudflare WARP y pulsa sobre el switch para habilitar el servicio. 3. Ahora debes apuntar el proxy del navegador a Cloudflare WARP, la configuración del navegador es similar a esta para el caso de navegadores basados en Firefox. Una vez hecho, deberías poder acceder a la guía de MiniBolt sin problemas. Si tienes dudas, déjalas en comentarios e intentaré resolverlas. Más info AQUÍ.

~> Proxifica tu navegador para usar la red de Tor, o utiliza el navegador oficial de Tor (recomendado).

La conclusión
Estos hechos ponen en tela de juicio los principios fundamentales de la neutralidad de la red, pilares esenciales de la Declaración de Independencia del Ciberespacio que defiende un internet libre, sin restricciones ni censura. Dichos principios se han visto quebrantados sin precedentes en este país, confirmando que ese futuro distópico que muchos negaban, ya es una realidad.
Es momento de actuar y estar preparados: debemos impulsar el desarrollo y la difusión de las herramientas anticensura que tenemos a nuestro alcance, protegiendo así la libertad digital y asegurando un acceso equitativo a la información para todos
Este compromiso es uno de los pilares fundamentales de MiniBolt, lo que convierte este desafío en una oportunidad para poner a prueba las soluciones anticensura ya disponibles, así como las que están en camino.
¡Censúrame si puedes, legislador! ¡La lucha por la privacidad y la libertad en Internet ya está en marcha!

Fuentes: * https://bandaancha.eu/articulos/movistar-o2-deja-clientes-sin-acceso-11239 * https://bandaancha.eu/articulos/esta-nueva-sentencia-autoriza-bloqueos-11257 * https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958 * https://bandaancha.eu/articulos/como-activar-ech-chrome-acceder-webs-10689 * https://comunidad.movistar.es/t5/Soporte-Fibra-y-ADSL/Problema-con-web-que-usan-Cloudflare/td-p/5218007
-
 @ 6bae33c8:607272e8
2025-03-25 11:03:28
@ 6bae33c8:607272e8
2025-03-25 11:03:28I try to make these bold enough that I get most of them wrong. If you’re not getting most wrong, they’re not bold enough! Hits from last year included Teoscar Hernandez being the Marcel Ozuna of 2024 and Shohei Ohtani’s gambling scandal getting memory-holed totally. Misses include Walker Buehler > Tarik Skubal and Spencer Torkelson > Vlad Guerrero. As I said, the predictions have to be bold!
Also, these are hunches, the explanations for which are largely irrelevant. The relevant information is priced into ADP, so while I’ll justify it one way or another, it’s the prediction itself, not the explanation that matters.
1, Alex Bregman is top-five in AL MVP voting
This just feels like a perfect fit. Bregman rakes at Fenway (1.240 career OPS), and he rarely strikes out. I could see a .300-plus batting average with 30 home runs. The Red Sox upgraded their pitching too, and after the Yankees lost Gerrit Cole and Juan Soto, have a good chance to win the AL East.
2. Bo Bichette outperforms Mookie Betts
Granted Betts is sick right now and lost a ton of weight, but he was still going in the second round of NFBC Mains, while Bichette was going in Rounds 8-9. Bichette was hurt last year, but prior to that he was a star, is in his age 27 season and has four home runs and a .373 average in Spring Training. I’m sick that I didn’t get any shares (took Bregman over him in the Main.)
3. Chris Sale finishes as a top-5 starter again
This might not sound that bold because he’s SP6 by ADP, but every pitcher except maybe Paul Skenes and Skubal are underdogs to be top-five, given the volatility of the position. I love veterans in their mid-30s finding it again, usually they have 2-3 years of good before age and injury catch up again. It reminds me of Justin Verlander who hit a rough patch before righting the ship for several elite years.
4. Tyler Glasnow finishes as top-3 in NL CY Young votes
My comp for Glasnow is Randy Johnson, another tall lefty who battled injuries in his 20s before settling down to become one of the GOATS. Glasnow managed 135 IP last year and if he ups it to 165, he’ll be in the CY mix on the Dodgers.
5. Cody Bellinger hits 40 homers
A pull hitter with a high fly ball rate, Bellinger is perfect for Yankee Stadium. He’ll have to stay healthy, of course, but he’s still just 29 — won’t turn 30 until July — and is primed for the second best year of his career (he won’t top 2019.)
6. At least one of the following veteran pitchers has a top-five CY finish: Justin Verlander, Max Scherzer, Kevin Gausman, Walker Buehler, Sandy Alcantara or Carlos Rodon.
Pitchers who were once elite still own most of their skills, health permitting. While Scherzer and Verlander have lost velocity, knowing how to pitch is sufficient above a certain minimum threshold.
7. Jackson Chourio goes 30-30-.300
Chourio hit over .300 for the final four months of the season, once the Brewers stopped pulling him in and out of the lineup. The steals should be easy for him with a full season of at-bats, and the power should be there too in that park.
8. Hunter Brown finishes top-five in AL CY voting
After a rough start, Brown was one of the best pitchers in the league last year with a 2.31 ERA over the last four months. He’s in a good park, in the right division (though the A’s home park got a lot worse) and on a good enough team for run support purposes.
9. Aroldis Chapman gets more saves than Jhoan Duran
Chapman is still throwing 99 and landed a job on the much-improved Red Sox, while Duran, who took nine losses last year, has Griffin Jax behind him. I know Chapman’s control has been bad the last few years, but I have a hunch the veteran warhorse has a comeback year.
10. Some of these predictions will be wrong
I’ll pay the cost of never going 10-for-10 to make sure I don’t go 0-for-10.
-
 @ 7da115b6:7d3e46ae
2025-03-25 11:00:01
@ 7da115b6:7d3e46ae
2025-03-25 11:00:01What Happened?
Sadly, some news came to us in the last couple of days, news that has exploded our plans like a bombshell. As you know from previous posts, my family and I had found the property of our dreams, within the price range that suited us. The only issue was that we had to sell our rental property to be able to purchase the land we wanted to develop for our homestead. At the time, it wasn't an issue.
With a few phone calls and some discussion with the local Council; the Realtor; the Vendors, and the bank, we were on our way. We made an offer, and it was accepted, contingent on our rental property selling. Our offer expires this Friday, and the likelihood of it selling before then, is slim. That leaves us 3 days to come up with the $130,000 we need to secure the property.
"So why not just extend the offer?" I hear you say. Well, that's a fair point - We did. The extension runs out this Friday. Can we extend on the extension? Legally, yes. but here's the rub:
A counter offer has been put forward.
This basically means, that without having the money available by the end of the offer extension, the Vendor is going to take the counter offer.
That's Not So Bad... Right?
Yes, and no.
Unfortunately, we've spend thousands of dollars on reports; valuations; building research and site inspections. This means all of the plans, money and time that we've invested so far is going to be lost. Yes yes, you're right of course, it's our own fault for getting so financially and emotionally invested in the first place. Lesson learned.
I think that the hardest part of it all, was breaking it to my wife. She had already started designing her gardens, and had dreams of watching our homestead grow. The look of utter defeat on her face was gut wrenching. I felt as though I had failed her, and torn away the dream we had built together. She and I had lost our dream in the course of a single phone call. It hit both of us hard.
It's been 24 hours now, and the pain is real. I don't want to eat or go to work, I don't want to talk to anyone. I just want to lay down on my wife's lap and close my eyes until it's over. Deep down inside, I know it's a childish reaction, but that doesn't make it any less of a slap across the face.
The Light at the End of the Tunnel
Cliche, I know, but there may be a little glimmer of light on the horizon. If we do sell our rental property, we will have money to play with. This means we can buy a crappy little Ute and caravan, and go exploring our country. Perhaps stop at a few places that look nice, and see if they're places we could settle. If we spend a few months just looking around, and find somewhere homely, then we can stay for a while at a local caravan park, and look for a property that may be suitable.
At the very least, it would mean that we can escape our shit jobs, which has been the biggest goal from the beginning.
Fingers crossed...
-
 @ 7da115b6:7d3e46ae
2025-03-25 10:55:04
@ 7da115b6:7d3e46ae
2025-03-25 10:55:04Originally written and posted on the 12th of December, 2024
Emotionally, it's been challenging to say the least, and the heat just exacerbates the frustration. But don't let that fool you; we've made significant progress. We found our dream property over two months ago for $130,000. 3 hectares of land, but 2 hectares of it is unusable. This was perfectly okay with us as it's going to be a massive effort for one person anyway.
Two months ago, we put in an offer and they accepted it. However, we are not well off by any means; most weeks, we just scrape by. We have two properties - a property in the Far North that we've been renting out to pay the mortgage ($70,000 remaining), and the one we live in which has almost the entire mortgage outstanding.
So how can we afford another property? Well it's no simple feat! First, we need to sell our Rental Property for around $400,000 (a reasonable market rate). Once that sells, about $170,000 in equity gets transferred to the mortgage of the property we're currently living in. After paying off the last of the mortgage on the rental property and shifting the equity to our current property, that will leave us with almost nothing after legal fees and real estate agent fees.
This amount remaining barely covers the cost of the property we put an offer on - our dream property. It's a humbling experience realizing just how far we still have to go in this journey towards self-sufficiency.
It's a sober reminder that we can't rush it, but should rather embrace each step along the way. For better or for worse, we must adapt and learn from every situation as it comes our way. After all, we can only control what's within our reach; the rest is just a matter of time and patience.
Perhaps it's not about achieving self-sufficiency, but truly embracing the journey itself. The path towards that dream property we've been longing for may take longer than expected, but as long as we have each other and keep pushing forward, I can't think of anything more rewarding than seeing our vision unfold step by step.
I have to remember to cherish the memories and experiences along this road, because it's those moments that will truly make the journey worthwhile.
-
 @ 7da115b6:7d3e46ae
2025-03-25 10:52:00
@ 7da115b6:7d3e46ae
2025-03-25 10:52:00Originally written and posted on the 10th of March, 2025
Safety
The first reason that comes to mind is safety. Violent crime has become a recurring theme in our town, with statistics showing a rise in cases such as burglaries and general homicides. These changes have made us acutely aware of the importance of providing a secure environment for our family. As our children grow, we yearn for them to experience not just safety, but also a sense of stability that comes with it.
The thought of crime often makes me reflect on moments like the domestic violence and murder within throwing distance of our current home, or the attempted mugging and homicide at a nearby petrol station. These incidents have sparked a desire for a place where our family can feel more secure and enjoy the peace of mind that comes with knowing they're safe. I hope that growing up in a safe environment will instill confidence and security in my kids as they navigate life. This pursuit of safety is not just about protecting my loved ones; it’s about creating a foundation where they can thrive and feel secure in their surroundings, allowing them to focus on their growth and aspirations without the constant awareness of potential danger.
Cost of Living
The cost of living has been another pivotal factor in our decision to move. Over time, we’ve noticed how the city’s expenses, from petrol to groceries, have steadily increased, making every purchase a mindful choice. The rising costs of utilities, transportation, and daily essentials have become a significant part of our budget, leaving us wondering if there’s room for more than just the basics. While the city offers many amenities, we’ve found ourselves seeking a lifestyle that aligns with our values and allows us to live comfortably without constant financial strain.
The cost of groceries has also become a major consideration. As prices rise, even simple trips to the store have us thinking about every purchase. We’ve found ourselves choosing between brands or quantities to stay within our budget, which has made us appreciate the idea of growing some of our own food.
While we love the idea of the cultural and social offerings of city life, the reality is that we spend more time trying to stretch our weekly budget to make ends meet, than we do enjoying the fruits of our labor. We’re looking forward to a place where we can manage our budget comfortably, while still having access to the amenities we need. This doesn’t mean we’re leaving behind everything we’ve grown accustomed to; it’s about finding a balance—a home that allows us to live fully without feeling constrained by expenses.
Our decision to move isn't about wanting to be one with nature or making a statement; it’s more about practicality. Owning a freehold property gives us the stability we need, allowing us to live sustainably without feeling tied down by expenses. This choice aligns with our values and offers a sense of freedom, not because we're trying to escape something, but because it supports the life we want for ourselves and our family. We’ve worked hard to pay down our mortgages, but now we’re ready for the next step—owning our own land that we can build upon.
We’re not looking to simplify just because we want to be closer to nature; rather, we see this move as an opportunity to create a lifestyle that’s more in tune with our needs. By growing our own food and living in a clean, natural environment, we’re prioritizing sustainability without compromising on what matters most—our family’s future and well-being. It’s about creating a home that reflects our values, not just embracing change for the sake of being different.
Educational Opportunities
Our oldest child’s education is another driving force behind this move. We’ve discovered that the place we’re moving to offers a University with "fees-free" options, which will provide him with an opportunity to pursue his studies without the burden of tuition costs. This not only eases our financial concerns but also gives us peace of mind knowing he can focus on his education without added stress. It’s a decision that aligns with our aspirations for his future and our family's well-being, hoping he can thrive in an environment that supports his academic journey and personal growth.
Also, our youngest child is going to have the opportunity to raise the animals he’s so enamored with, such as chickens; dogs; pigs, and maybe even a couple of sheep. I want these experiences to help him to learn by doing, fostering a sense of responsibility and connection with where our food comes from. By caring for these creatures, we hope he’ll develop life skills that will help him grow into his own skin as he gets older. It’s a chance for him to explore his passions and build confidence in a hands-on way.
Freedom
Space has become something we truly appreciate, especially with our kids and pets. We’re eager for them to have more room to roam and explore freely. The privacy that a rural setting offers is high on our list of needs because living in the city often feels like we're always surrounded by others. It's not uncommon to bump into neighbors or find ourselves at loggerheads over simple things like car parks. This constant interaction, while part of city life, can sometimes feel overwhelming.
But it's not just us - our current place of employment also experiences issues with neighboring businesses, and it’s the employees who end up feeling the impact. It feels as if everyone is out for themselves, and are incapable of thinking about how their actions affect others.The city environment feels cramped and extremely claustrophobic, making us yearn for more personal space. We’re looking forward to the freedom of having our own large property where we can enjoy peace and quiet. It’s exciting to think about the possibilities, like building a barn or adding bee hives, and even sinking a water well as we please.
Food & Gardening
The idea of growing our own food is another exciting prospect that we're eager to explore. We’re looking forward to cultivating fresh produce in our garden, which will not only provide healthier options for our family but also add variety and freshness to our meals. It will be a major undertaking for us. While I personally have some understanding of growing and harvesting simple crops like potatoes and cabbage, I am deeply aware of my lack of knowledge and experience. It will take years for me to actually become proficient. We’re excited to teach our kids where their food comes from and instill an appreciation for sustainable living. Growing our own produce aligns with our desire for a more natural, self-sufficient lifestyle, offering us the joy of seeing the fruits of our labor in our garden.
Exercise & General Wellness
Living in a bustling city has its perks, but it has also take a toll on our sense of well-being. The daily grind often leaves us feeling mentally and emotionally drained, leaving little room for relaxation and physical activity. With the convenience of modern life comes a faster pace, which, while beneficial, frequently feels overwhelming. We long for moments to pause, breathe in fresh air, and reconnect with ourselves.
I think that the desire for more exercise and fresh air, is a natural response to the our current lifestyle. The city’s vibrant atmosphere and endless opportunities often come at the expense of personal time and the chance to enjoy relax. By seeking a new environment, We're looking for a balanced life for our family, where we can revitalize their minds and bodies through simple yet essential activities like walking around the property or the exercise of working the land. This shift is not just about changing scenery; it’s about creating a lifestyle that supports our overall well-being and allows for moments of peace away from the hustle and bustle.
In conclusion, this move is about more than just changing scenery; it’s about creating a home that embodies our values—safety, education, sustainability, and well-being for our family. It’s a step towards a future where we can thrive in an environment that supports our growth and aspirations.
-
 @ ecda4328:1278f072
2025-03-25 10:00:52
@ ecda4328:1278f072
2025-03-25 10:00:52Kubernetes and Linux Swap: A Practical Perspective
After reviewing kernel documentation on swap management (e.g., Linux Swap Management), KEP-2400 (Kubernetes Node Memory Swap Support), and community discussions like this post on ServerFault, it's clear that the topic of swap usage in modern systems—especially Kubernetes environments—is nuanced and often contentious. Here's a practical synthesis of the discussion.
The Rationale for Disabling Swap
We disable SWAP on our Linux servers to ensure stable and predictable performance by relying on available RAM, avoiding the performance degradation and unnecessary I/O caused by SWAP usage. If an application runs out of memory, it’s usually due to insufficient RAM allocation or a memory leak, and enabling SWAP only worsens performance for other applications. It's more efficient to let a leaking app restart than to rely on SWAP to prevent OOM crashes.
With modern platforms like Kubernetes, memory requests and limits are enforced, ensuring apps use only the RAM allocated to them, while avoiding overcommitment to prevent resource exhaustion.
Additionally, disabling swap may protect data from data remanence attacks, where sensitive information could potentially be recovered from the swap space even after a process terminates.
Theoretical Capability vs. Practical Deployment
Linux provides a powerful and flexible memory subsystem. With proper tuning (e.g., swappiness, memory pinning, cgroups), it's technically possible to make swap usage efficient and targeted. Seasoned sysadmins often argue that disabling swap entirely is a lazy shortcut—an avoidance of learning how to use the tools properly.
But Kubernetes is not a traditional system. It's an orchestrated environment that favors predictability, fail-fast behavior, and clear isolation between workloads. Within this model:
- Memory requests and limits are declared explicitly.
- The scheduler makes decisions based on RAM availability, not total virtual memory (RAM + swap).
- Swap introduces non-deterministic performance characteristics that conflict with Kubernetes' goals.
So while the kernel supports intelligent swap usage, Kubernetes intentionally sidesteps that complexity.
Why Disable Swap in Kubernetes?
-
Deterministic Failure > Degraded Performance\ If a pod exceeds its memory allocation, it should fail fast — not get throttled into slow oblivion due to swap. This behavior surfaces bugs (like memory leaks or poor sizing) early.
-
Transparency & Observability\ With swap disabled, memory issues are clearer to diagnose. Swap obfuscates root causes and can make a healthy-looking node behave erratically.
-
Performance Consistency\ Swap causes I/O overhead. One noisy pod using swap can impact unrelated workloads on the same node — even if they’re within their resource limits.
-
Kubernetes Doesn’t Manage Swap Well\ Kubelet has historically lacked intelligence around swap. As of today, Kubernetes still doesn't support swap-aware scheduling or per-container swap control.
-
Statelessness is the Norm\ Most containerized workloads are designed to be ephemeral. Restarting a pod is usually preferable to letting it hang in a degraded state.
"But Swap Can Be Useful..."
Yes — for certain workloads (e.g., in-memory databases, caching layers, legacy systems), there may be valid reasons to keep swap enabled. In such cases, you'd need:
- Fine-tuned
vm.swappiness - Memory pinning and cgroup-based control
- Swap-aware monitoring and alerting
- Custom kubelet/systemd integration
That's possible, but not standard practice — and for good reason.
Future Considerations
Recent Kubernetes releases have introduced experimental swap support via KEP-2400. While this provides more flexibility for advanced use cases — particularly Burstable QoS pods on cgroupsv2 — swap remains disabled by default and is not generally recommended for production workloads unless carefully planned. The rationale outlined in this article remains applicable to most Kubernetes operators, especially in multi-tenant and performance-sensitive environments.
Even the Kubernetes maintainers acknowledge the inherent trade-offs of enabling swap. As noted in KEP-2400's Risks and Mitigations section, swap introduces unpredictability, can severely degrade performance compared to RAM, and complicates Kubernetes' resource accounting — increasing the risk of noisy neighbors and unexpected scheduling behavior.
Some argue that with emerging technologies like non-volatile memory (e.g., Intel Optane/XPoint), swap may become viable again. These systems promise near-RAM speed with large capacity, offering hybrid memory models. But these are not widely deployed or supported in mainstream Kubernetes environments yet.
Conclusion
Disabling swap in Kubernetes is not a lazy hack — it’s a strategic tradeoff. It improves transparency, predictability, and system integrity in multi-tenant, containerized environments. While the kernel allows for more advanced configurations, Kubernetes intentionally simplifies memory handling for the sake of reliability.
If we want to revisit swap usage, it should come with serious planning: proper instrumentation, swap-aware observability, and potentially upstream K8s improvements. Until then, disabling swap remains the sane default.
-
 @ 7d33ba57:1b82db35
2025-03-25 09:38:27
@ 7d33ba57:1b82db35
2025-03-25 09:38:27Located on the Costa de la Luz, Chipiona is a charming seaside town in Cádiz province, known for its stunning beaches, iconic lighthouse, and delicious local wines. It’s a perfect destination for those seeking relaxation, history, and Andalusian charm.
🏖️ Top Things to See & Do in Chipiona
1️⃣ Chipiona Lighthouse (Faro de Chipiona) 💡
- The tallest lighthouse in Spain (69 meters), built in 1867.
- Climb 322 steps for breathtaking views of the Atlantic Ocean.
- Used to guide ships through the Gulf of Cádiz for centuries.
2️⃣ Playa de Regla 🏝️
- The most famous beach in Chipiona, known for its golden sand and calm waters.
- Perfect for sunbathing, swimming, and long walks along the shore.
- Surrounded by beach bars (chiringuitos) and seafood restaurants.
3️⃣ Santuario de Nuestra Señora de Regla ⛪
- A beautiful neo-Gothic monastery near the beach.
- Home to the Virgen de Regla, the town’s patron saint.
- A site of religious pilgrimages, especially in September.
4️⃣ Las Corrales de Pesca 🎣
- Ancient fishing structures made of stone walls in the sea, dating back to Roman times.
- A unique traditional fishing method, still in use today.
- Guided tours are available to learn about their history.
5️⃣ Bodega César Florido 🍷
- Visit one of the oldest wineries in Chipiona, famous for Moscatel wine.
- Enjoy a wine tasting tour and learn about the local winemaking tradition.
6️⃣ Paseo Marítimo & Sunset Views 🌅
- A scenic beachfront promenade, ideal for an evening stroll.
- Watch the sunset over the Atlantic Ocean, one of the most beautiful in Andalusia.
🍽️ What to Eat in Chipiona
- Langostinos de Sanlúcar – Delicious local prawns, best with a glass of Manzanilla wine 🦐🍷
- Tortillitas de camarones – Crispy shrimp fritters, a Cádiz specialty 🥞🦐
- Chocos a la plancha – Grilled cuttlefish with olive oil and lemon 🦑
- Pescaíto frito – A mix of fried fresh fish, perfect for a beachside meal 🐟
- Moscatel de Chipiona – A sweet dessert wine, famous in the region 🍷

🚗 How to Get to Chipiona
🚘 By Car: ~30 min from Cádiz, 1 hr from Seville, 2 hrs from Málaga
🚆 By Train: Closest stations in El Puerto de Santa María or Jerez de la Frontera
🚌 By Bus: Regular buses from Cádiz, Jerez, and Seville
✈️ By Air: Nearest airport is Jerez de la Frontera (XRY) (~40 min away)💡 Tips for Visiting Chipiona
✅ Best time to visit? Spring & summer for beach weather, September for festivals 🌞
✅ Try a Moscatel wine tour – The local wineries are world-famous 🍷
✅ Bring comfortable shoes – If climbing the lighthouse 👟
✅ Visit in September for the Fiestas de la Virgen de Regla, a unique cultural experience 🎉 -
 @ da0b9bc3:4e30a4a9
2025-03-25 09:14:07
@ da0b9bc3:4e30a4a9
2025-03-25 09:14:07Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/924287
-
 @ 220522c2:61e18cb4
2025-03-25 06:57:24
@ 220522c2:61e18cb4
2025-03-25 06:57:24
-
 @ 21335073:a244b1ad
2025-03-18 20:47:50
@ 21335073:a244b1ad
2025-03-18 20:47:50Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ d560dbc2:bbd59238
2025-03-25 05:29:36
@ d560dbc2:bbd59238
2025-03-25 05:29:36Hey! Today, I’m diving into the 2-5 Rule—a unique task management method that’s all about timing, not planning. It powers TaskforUs, a beta platform that’s changing how we prioritize tasks. Grab a coffee, and let’s get started!
What Is the 2-5 Rule?
The 2-5 Rule is a task management approach that focuses on when to act on a task rather than creating a detailed plan. Every task has a “time unit” (days, weeks, months, or years), and you should act within 2 to 5 of those units. This “sweet spot” ensures that you’re neither rushing nor neglecting tasks.
Examples:
- Daily tasks: (e.g., “Do cardio”) – Act every 2-5 days.
- Weekly tasks: (e.g., “Meet a friend”) – Act every 2-5 weeks.
- Monthly tasks: (e.g., “Review budget”) – Act every 2-5 months.
- Yearly tasks: (e.g., “Renew passport”) – Act every 2-5 years.
You don’t plan the exact time to do the task—just enter it into TaskforUs, set the time unit, and provide either the last date you acted on it or a fixed due date. The system prioritizes it for you, making it an anti-planning method.
How Does It Work in Practice?
Example 1: Renewing Your Passport
-
Scenario:
You get your passport today (March 24, 2025). -
Action:
Add the task “Renew passport” to TaskforUs with a yearly time unit and set the “last act date” as today. -
Outcome:
The task starts low on your priority list but climbs over time. After 2 years, it begins to rise; by 5 years, it’s near the top—nudging you to act before your passport expires.
Alternatively, use Fix Mode to set the expiration date (e.g., March 24, 2030) so the task climbs in priority as the date approaches.
Example 2: Meeting Uncle Lars Regularly
-
Scenario:
You want to meet your Uncle Lars roughly 10 times a year (about once every 5 weeks). -
Action:
Add the task “Meet Uncle Lars” with a weekly time unit (to provide flexibility) and set the “last act date” as the most recent meeting (e.g., March 1, 2025). -
Outcome:
Over time, the task slowly climbs in your priority list. After 2 weeks, it starts gaining focus; by 5 weeks, it becomes urgent—prompting you to schedule the next meeting.
No detailed planning is required—you simply add the task, and the 2-5 Rule does the rest.
The Psychology Behind the 2-5 Rule
The 2-5 Rule isn’t just a clever idea—it’s grounded in psychology and behavioral science. Here’s why it works so well:
-
It Reduces Decision Fatigue
Constantly deciding when to do each task can be exhausting. The 2-5 Rule automates prioritization, so you don’t have to think about when to act. TaskforUs surfaces the right task at the right time, freeing up mental energy for doing the work. -
It Aligns with Natural Rhythms
Humans thrive on rhythm and consistency. Behavioral science shows that after 2 time units, a task starts to feel pressing, but by 5 units, it’s at risk of being neglected. The 2-5 window captures this natural sense of urgency. -
It Taps into the Zeigarnik Effect
This psychological principle states that uncompleted tasks are remembered better than completed ones. As a task’s due window approaches, it naturally rises in priority—keeping it top of mind. -
It Prevents Over-Planning Stress
Detailed scheduling can be stressful, especially when life is unpredictable. The anti-planning nature of the 2-5 Rule removes this burden: you simply enter your task and let the system remind you when it’s time to act.
The Structure of TaskforUs: Bringing the 2-5 Rule to Life
TaskforUs is a web-based platform (currently in beta) that makes the 2-5 Rule actionable:
-
Add Tasks Easily:
Simply enter a task, set its time unit (days, weeks, months, or years), and provide the last act date or a fixed due date for Fix Mode tasks. -
Top Task:
TaskforUs automatically highlights your most urgent task based on the 2-5 Rule, telling you exactly what to do right now. -
Focus Mode:
See your top 3 tasks (or adjust the number) for distraction-free productivity. -
Fix Mode:
For date-specific tasks (e.g., “Wish Alex a happy birthday”), set the due date and watch the task climb in priority as the day approaches, peaking on the day itself. -
Category Filtering and Archiving:
Organize tasks into categories (e.g., Work, Personal) and archive completed tasks to keep your list clean. -
Export Tasks:
Download your tasks as a CSV file for backup or analysis.
TaskforUs takes the 2-5 Rule’s anti-planning philosophy and makes it seamless, ensuring you always know what to do next without the mental load of scheduling.
Why the 2-5 Rule Works: A Game-Changer for Task Management
The 2-5 Rule stands out because it addresses common pain points in task management:
-
No More Overwhelm:
By focusing on one top task (or a few in Focus Mode), you avoid the clutter of a long to-do list. -
Effortless Prioritization:
The rule automates the decision of what to do next, reducing stress and boosting productivity. -
Never Miss a Deadline:
With Fix Mode, date-specific tasks like passport renewals or birthdays rise to the top at the right time. -
Flexibility:
The 2-to-5 window gives you room to act when it suits you—without rigid deadlines.
Try the 2-5 Rule with TaskforUs
The 2-5 Rule is a fresh take on task management that balances short-term habits with long-term goals—without the burden of meticulous planning. TaskforUs makes it easy to implement, and as a beta user, you can help shape its future.
Here’s why you should try it:
-
No Planning Needed:
Just add your tasks and let the system prioritize them automatically. -
Clarity:
Always know what to do right now—without the mental load of overthinking. -
Flexibility:
The 2-to-5 window gives you the right balance between urgency and ease. -
Reliability:
Fix Mode ensures you never miss critical dates. -
Be Part of the Beta:
Your feedback helps improve TaskforUs as it evolves.
Take Control of Your Tasks Today
The 2-5 Rule is more than a productivity hack—it’s a new way to manage tasks by focusing on timing rather than rigid plans. Ready to say goodbye to overwhelm and hello to effortless prioritization?
Sign up for TaskforUs at task4.us and experience the 2-5 Rule in action.
Your tasks, perfectly timed—without a plan in sight. -
 @ a39d19ec:3d88f61e
2025-03-18 17:16:50
@ a39d19ec:3d88f61e
2025-03-18 17:16:50Nun da das deutsche Bundesregime den Ruin Deutschlands beschlossen hat, der sehr wahrscheinlich mit dem Werkzeug des Geld druckens "finanziert" wird, kamen mir so viele Gedanken zur Geldmengenausweitung, dass ich diese für einmal niedergeschrieben habe.
Die Ausweitung der Geldmenge führt aus klassischer wirtschaftlicher Sicht immer zu Preissteigerungen, weil mehr Geld im Umlauf auf eine begrenzte Menge an Gütern trifft. Dies lässt sich in mehreren Schritten analysieren:
1. Quantitätstheorie des Geldes
Die klassische Gleichung der Quantitätstheorie des Geldes lautet:
M • V = P • Y
wobei:
- M die Geldmenge ist,
- V die Umlaufgeschwindigkeit des Geldes,
- P das Preisniveau,
- Y die reale Wirtschaftsleistung (BIP).Wenn M steigt und V sowie Y konstant bleiben, muss P steigen – also Inflation entstehen.
2. Gütermenge bleibt begrenzt
Die Menge an real produzierten Gütern und Dienstleistungen wächst meist nur langsam im Vergleich zur Ausweitung der Geldmenge. Wenn die Geldmenge schneller steigt als die Produktionsgütermenge, führt dies dazu, dass mehr Geld für die gleiche Menge an Waren zur Verfügung steht – die Preise steigen.
3. Erwartungseffekte und Spekulation
Wenn Unternehmen und Haushalte erwarten, dass mehr Geld im Umlauf ist, da eine zentrale Planung es so wollte, können sie steigende Preise antizipieren. Unternehmen erhöhen ihre Preise vorab, und Arbeitnehmer fordern höhere Löhne. Dies kann eine sich selbst verstärkende Spirale auslösen.
4. Internationale Perspektive
Eine erhöhte Geldmenge kann die Währung abwerten, wenn andere Länder ihre Geldpolitik stabil halten. Eine schwächere Währung macht Importe teurer, was wiederum Preissteigerungen antreibt.
5. Kritik an der reinen Geldmengen-Theorie
Der Vollständigkeit halber muss erwähnt werden, dass die meisten modernen Ökonomen im Staatsauftrag argumentieren, dass Inflation nicht nur von der Geldmenge abhängt, sondern auch von der Nachfrage nach Geld (z. B. in einer Wirtschaftskrise). Dennoch zeigt die historische Erfahrung, dass eine unkontrollierte Geldmengenausweitung langfristig immer zu Preissteigerungen führt, wie etwa in der Hyperinflation der Weimarer Republik oder in Simbabwe.
-
 @ 7da115b6:7d3e46ae
2025-03-25 05:14:41
@ 7da115b6:7d3e46ae
2025-03-25 05:14:41Originally written and posted on the 21st of Sept, 2022
I'm about 6 months into the ownership of my first bike, since I was a teenager. It has most definitely been an interesting time. While I am truly enjoying riding, it's not been without it's hiccups.
The first real issue is that I don't have a great knowledge of motorcycle models, or their general history. My first ride was an 80cc Yamaha Jog, which could do 70 Km/h down hill with a tail wind. My second was a Yamaha DX100 (colloquially known as the "Flying Banana"), which I could start with the handle of a teaspoon, and was lost when the back tyre burst during a trip, resulting in a write-off (a story in of itself).
So a little background first. The reason I purchased a bike, is mostly for financial reasons. While there is an argument to be made that it's more expensive to ride than drive, I did a ton of math, and came to the conclusion that it actually works out cheaper, considering my circumstances. When factoring in the massive rise in fuel costs; the far lower insurance costs; and lower maintenance costs (due to being able to maintain it reasonably well on my own). It seemed that because I do long trips of around 400 Km every couple of weeks, it was a sound option. Also, being middle aged, I ended up having to go back and sit my motorcycle licence, as with my previous bikes, it was in a time where riding dirty on small displacement bikes wasn't really noticed by the cops (yes, that does indeed make me a middle aged learner rider).
When researching bikes, I made a few things a priority:
- Small displacement
- Aesthetically pleasing
- Easily repairable
- Cheap maintenance
- Reliability
- Fuel efficient
nb. I didn't include things like performance or top speed, because they were mostly irrelevant to my needs at the time.
In the end, it worked out that the Kawasaki Ninja 250 fit all of the criteria I had set. It was about then that I set out to find a good example of the model, at a reasonable price.
I delved into the subject with gusto, looking at the Trademe sales, and researching as best as I could. I ran across the Ninja250 Wiki and found a thriving community built around these interesting little bikes. While I didn't interact directly with the community, I did find the compiled resources invaluable for my purposes. They've pulled together schematics, technical manuals, replacement parts lists, tips & tricks and a ton of general information. Very handy.
Unfortunately, Kawasaki have been a little liberal with the "Ninja" moniker, and it seems like they enjoyed slapping the label on a ton of different models. It got extremely confusing in a very short period of time. In the end, I found a listing for a 2007 Ninja 250, that looked really clean for its age, with only 30,000Kms on the clock. Being the 2007 model, it was the last of the dual carb bikes, before they switched to Electronic Fuel Injection. This appealed to me, because it lowered the bar for maintenance.
It seemed like the perfect option for me, so I got in contact with the owner, and we negotiated a price. I looked over the bike, and in my inexperience, I missed some crucial details that a more experienced rider would have noticed (I'll get to those details shortly). After a quick ride on my newly minted Learners Licence, I found the power was decent and it rode well. I checked for things like frame fatigue, engine noise, drops in power, exhaust leaks, tyre tread, oil leaks and more.
The owner seemed trustworthy, so when he told me that "It runs like a dream, and it's never needed any work aside from a replacement faring", I believed him. In hind sight, I seriously should have realised the red flag about it needing new faring.
This is where we get to the details I missed.
Firstly, It looks like the Oil Filter had never been changed, but to cover this fact, they did an oil change just before the sale, so it looked clean.
Secondly, the fuel filter had never been changed, so was full of crud. Because it's hidden in the carb end of the fuel line, you cant see it on a cursory look.
Thirdly, someone had removed the air filter, and just never bothered to put it back or replace it. Unfortunately, it's under the fuel tank, so you cant see it without removing the tank.
Fourth and finally, the Faring. So it turns out that the bike had definitely been laid down at some point. My naivety and excitement blinded me to what was obvious. The clutch handle was scratched to sin, the tail bar has scrapes along one corner, and the foot pegs had been replaced.
Again, looking back, how could I not have seen these things? I'm kicking myself, but now that I have it, I just have to deal with the consequences.
I'm disappointed in the seller for not disclosing these issues, and to say that I was cursing his name when I found out about these things, is a definite understatement. I know that I should have been more diligent, but it calls into question my judgement. I feel a little ripped off by people like this, and am starting to question a lot of decisions I wouldn't normally hesitate to make.
Anyway, after a lot more research it turns out it's not even an EX250, which is what the previous owner told me. It is in fact a GPX250, which has a completely different set of parts. This was a true eye opener, and led me to order parts that are completely incompatible with the bike. When I finally found out the correct model, I was able to move forward.
Since having the bike, I've lubed the chain multiple times (it looks like it had never been done); I've replaced the oil filter and done an oil change; ripped out the silly fuel filter and added an in-line gravity fed one that is transparent and easy to view; and replaced the air filter.
It seems to be running better now, and there is more to be done, but I'm sad that it has come to this. I never should have listened to the previous owner, let alone trusted him. I have learned my lesson, and will be far more vigilant in the future.
-
 @ e5de992e:4a95ef85
2025-03-25 05:00:45
@ e5de992e:4a95ef85
2025-03-25 05:00:45Global financial markets are experiencing significant movements influenced by recent developments in trade policies, economic data releases, and geopolitical events.
U.S. Stock Market Performance
On March 24, 2025, U.S. stock markets rallied sharply, buoyed by optimism surrounding potential easing of forthcoming tariffs:
-
Dow Jones Industrial Average (DJIA):
Rose by nearly 600 points (1.4%), closing at 42,583.32. -
S&P 500:
Increased by 1.8%, ending the session at 5,767.57 points. -
Nasdaq Composite:
Advanced by 2.3%, finishing at 18,188.59 points.
These gains were led by significant advances in the technology sector, with notable performances from companies like Tesla, which surged 12%, and Nvidia, which gained 3.2%.
U.S. Futures Market
As of the latest data, U.S. stock futures are exhibiting slight fluctuations:
-
Dow Jones Futures:
Indicated a modest decline, reflecting investor caution ahead of upcoming economic data releases. -
S&P 500 Futures:
Showed minimal movement, suggesting tentative market sentiment. -
Nasdaq Futures:
Displayed slight volatility, influenced by recent tech sector performances.
Key Factors and Events Influencing U.S. Markets
Trade Policy Developments
- Recent market rallies were largely driven by reports that the U.S. administration plans to implement more targeted tariffs than initially feared.
- Certain sectors such as automobiles and semiconductors may be exempted, alleviating investor concerns about trade policies impacting economic growth.
Economic Data Releases
- Investors are closely monitoring upcoming economic indicators, including the Consumer Confidence Index and the Personal Consumption Expenditures (PCE) index.
- These indicators will help gauge the health of the economy and inform potential implications for monetary policy.
Federal Reserve's Monetary Policy
- The Federal Reserve's recent decision to maintain interest rates—along with its revised economic outlook—continues to influence market sentiment.
- This policy stance is particularly relevant in relation to inflation expectations and growth projections.
Global Stock Indices Performance
International markets have shown mixed reactions in response to U.S. trade policy developments and regional economic data:
-
Germany's DAX:
Experienced modest gains amid cautious optimism over global trade discussions. -
UK's FTSE 100:
Edged higher, supported by strength in commodity-related sectors. -
Euro Stoxx 50:
Advanced, driven by positive corporate earnings reports and easing trade tensions. -
Japan's Nikkei 225:
Rose by over 1%, mirroring Wall Street’s upbeat performance and optimism regarding U.S. tariff policies. -
Hong Kong's Hang Seng:
Declined by 1%, impacted by profit-taking activities and ongoing trade uncertainties.
Cryptocurrency Market
The cryptocurrency market has exhibited volatility, with major digital assets experiencing price fluctuations:
-
Bitcoin (BTC):
Trading at approximately $84,481.00, down 1.82% from the previous close. -
Ethereum (ETH):
Priced around $1,987.26, reflecting a 2.18% decrease from the prior session.
These movements highlight the broader market's sensitivity to regulatory developments and macroeconomic factors affecting investor sentiment in the digital asset space.
Key Global Economic and Geopolitical Events
-
Trade Tensions and Tariff Policies:
Rapid escalation of trade barriers—reminiscent of protectionist measures from the 1930s—has raised concerns about long-term economic and diplomatic ramifications, including slower growth and heightened inflation. -
Central Bank Communications:
Statements from Federal Reserve officials and other central bank representatives are being closely scrutinized for future monetary policy directions. -
Corporate Earnings Reports:
Upcoming earnings releases from major corporations are expected to provide further clarity on sector health and broader economic conditions, influencing market dynamics in the near term.
Conclusion
Global financial markets are navigating a complex landscape shaped by trade policy developments, economic data releases, and geopolitical events. Investors are advised to remain vigilant and consider these factors when making informed decisions, as they are likely to continue influencing market behavior in the foreseeable future.
-
-
 @ bf7973ed:841ad12a
2025-03-25 04:19:41
@ bf7973ed:841ad12a
2025-03-25 04:19:41test
-
 @ 502ab02a:a2860397
2025-03-25 02:24:07
@ 502ab02a:a2860397
2025-03-25 02:24:07ต่อเนื่องจากมหากาพย์น้ำมันมะกอกปลอมนะครับ คนที่ปลอมแปลงน้ำมันมะกอกได้พัฒนาวิธีการต่าง ๆ เพื่อเลียนแบบคุณสมบัติของน้ำมันมะกอกแท้ ทำให้การตรวจสอบด้วยการแช่เย็นเพื่อดูการแข็งตัวอาจไม่สามารถยืนยันความบริสุทธิ์ได้อย่างแน่นอนแล้วหละครับ
คำแนะนำในการเลือกซื้อน้ำมันมะกอกจะแบ่งเป็นกว้างงงงงงงกว้าง 3 เรื่องคือ 1 ซื้อจากแหล่งที่เชื่อถือได้ เลือกซื้อน้ำมันมะกอกจากผู้ผลิตหรือร้านค้าที่มีความน่าเชื่อถือ และมีการรับรองคุณภาพจากหน่วยงานที่เกี่ยวข้อง ซึ่ง เชรี่ยละ ฝากเงินไว้กับคนอื่น 5555 2 ตรวจสอบฉลาก อ่านฉลากผลิตภัณฑ์อย่างละเอียด ตรวจสอบแหล่งที่มา วันที่ผลิต และวันที่หมดอายุ อันนี้คือที่เราจะคุยกันวันนี้ 3 สังเกตลักษณะของน้ำมัน น้ำมันมะกอกแท้มักมีสีและกลิ่นเฉพาะตัว หากพบว่าสีหรือกลิ่นผิดปกติ ควรพิจารณาก่อนซื้อ ตรงนี้นี่ต้องอาศัยความเจ็บปวดจากการพลาดเยอะๆ จะทำให้รู้ความแตกต่างครับ ซึ่ง not bad นะ
ไล่จากเรื่องเล็กก่อน คือ การสังเกตลักษณะน้ำมัน แบบที่นิยมสุุดคือ การแช่ตู้เย็นแล้วดูว่ามันแข็งไหม ที่เราสอนต่อๆกันมาคือ ถ้าแข็งก็คือดี ของแท้ แต่ แต่ แต่ ส่วนใหญ่แล้วการปลอมน้ำมันมะกอกเขาจะใช้หลากหลายวิธี แล้วแต่คนจะทำครับ อาทิเช่น การเจือปนสิ่งเหล่านี้ลงไปครับ - ไขมันเติมไฮโดรเจนบางส่วน ได้แก่พวกน้ำมันพืชราคาถูก เช่น น้ำมันถั่วเหลือง น้ำมันปาล์ม หรือคาโนลา มักถูกเติมไฮโดรเจนบางส่วนเพื่อเพิ่มอายุการเก็บรักษาอยู่แล้ว ต้นทุนต่ำกว่าน้ำมันมะกอกมาก หลายๆคนคงบอกว่า เอ้ย มันแช่เย็นแล้วไม่แข็งตัวนี่ ตรงนี้มีข้อมูลบอกว่า เขาใช้ไขมันทรานส์หรือไขมันเติมไฮโดรเจน โดยใช้หลักการทางเคมีที่ทำให้เนื้อสัมผัสของน้ำมันปลอมเลียนแบบพฤติกรรมของน้ำมันมะกอกแท้เมื่อถูกแช่เย็น บางที่ก็เติมน้ำมันมะพร้าวหรือน้ำมันปาล์ม อันนี้ต้นทุนต่ำทำง่ายเลยครับ เค้าใช้น้ำมันปาล์มโอเลอินที่มีการ ปรับแต่ง ด้วยการ เติมสารเติมแต่ง ทำให้ไขมันในน้ำมันมีลักษณะแข็งขึ้นและสามารถ ปรับจุดหลอมเหลว ให้สามารถแข็งตัวที่อุณหภูมิที่เย็นได้มากขึ้น - กรดไขมันอิ่มตัวสังเคราะห์ ประเภทกรดสเตียริกหรือกรดปาลมิติกสังเคราะห์เป็นผลิตภัณฑ์พลอยได้จากอุตสาหกรรมแปรรูปไขมันพืชและสัตว์ ราคาต่อหน่วยต่ำมาก โดยเฉพาะถ้าซื้อในปริมาณมาก - ไขมันจากสัตว์ อย่างเช่นไขมันหมูและน้ำมันปลาถูกกว่าน้ำมันมะกอก และสามารถหาได้จากอุตสาหกรรมแปรรูปอาหารที่มักมีของเหลือทิ้งในปริมาณมาก - ขี้ผึ้งพืช พวกขี้ผึ้ง Candelilla Wax หรือ Carnauba Wax ราคาถูกกว่าและสามารถใช้ในปริมาณน้อยเพื่อเลียนแบบคุณสมบัติทางกายภาพ - โมโนกลีเซอไรด์และไดกลีเซอไรด์ เป็นสารเติมแต่งที่ใช้ในอุตสาหกรรมอาหารอยู่แล้ว ต้นทุนต่ำมาก และช่วยให้น้ำมันมีเนื้อสัมผัสคล้ายน้ำมันมะกอก
ในข้อต่อมาจะรวมกันได้เลยครับ ฉลาก และ การรับรองคุณภาพ คือผมตัดเรื่องผู้ผลิตหรือร้านค้าออกไปเลย เพราะก็ไปดูเองได้ว่าแบรนด์เก่าแก่ เราก็จะเหมารวมไปเองว่าไม่น่าโกง 5555 เราข้ามมาอะไรที่พอจะมีหลักเกณฑ์ได้นะครับ short cut เลยคือ ตรารับรอง ใครจะดู DOP IGP USDA Organic อะไรผมไม่ค่อยสนใจครับ ผมว่าถ้าเป็นไปได้ข้ามไปดูนี่เลยครับ
 - International Olive Council (IOC) น้ำมันมะกอกที่ได้รับการรับรองจาก IOC เป็นการรับรองคุณภาพน้ำมันมะกอกที่ได้รับการตรวจสอบจากองค์กรที่มีมาตรฐานสากล
- COOC (California Olive Oil Council) สำหรับน้ำมันมะกอกที่ผลิตในแคลิฟอร์เนีย หรือในสหรัฐฯ จะมีการรับรองจาก COOC ที่ยืนยันว่าผ่านการตรวจสอบมาตรฐาน
- International Olive Council (IOC) น้ำมันมะกอกที่ได้รับการรับรองจาก IOC เป็นการรับรองคุณภาพน้ำมันมะกอกที่ได้รับการตรวจสอบจากองค์กรที่มีมาตรฐานสากล
- COOC (California Olive Oil Council) สำหรับน้ำมันมะกอกที่ผลิตในแคลิฟอร์เนีย หรือในสหรัฐฯ จะมีการรับรองจาก COOC ที่ยืนยันว่าผ่านการตรวจสอบมาตรฐานเรามาทำความเข้าใจรายละเอียดของน้ำมันมะกอกกันก่อนครับ เพื่อว่าตอนดูฉลากจะได้รู้ว่าทำไมต้องมีของพวกนี้ พันธุ์มะกอกที่ใช้ทำน้ำมันมะกอกนั้นเป็นตัวกำหนดรสชาติและกลิ่นหอมของน้ำมันมะกอก โดยมะกอกแต่ละสายพันธุ์ให้รสชาติแตกต่างกันครับ Arbequina (สเปน): กลิ่นผลไม้ มีรสคล้ายแอปเปิ้ลเขียว Koroneiki (กรีซ): เผ็ดร้อน มีรสพริกไทย Coratina (อิตาลี - Puglia): รสเข้ม เผ็ดร้อน มีรสขมติดปลายลิ้น Manzanilla cacereña (สเปน): หอมผลไม้ มีรสอัลมอนด์ แอปเปิ้ลเขียว Peranzana (อิตาลี - Puglia): รสชาติกลมกล่อม หอมหวานเล็กน้อย
- พื้นที่เพาะปลูกและผลิต ตัวนี้แหละครับ เอาไปทำตรา IGP เรียกเหมาๆว่า Geographical Origin น้ำมันมะกอกคุณภาพสูงจะระบุชัดเจนว่า มะกอกมาจากไหนและผลิตที่ไหน ถ้าฉลากไม่ระบุ แสดงว่าอาจเป็นน้ำมันมะกอกผสมจากหลายแหล่ง ซึ่งอาจมีคุณภาพต่ำ
- วันที่เก็บเกี่ยว น้ำมันมะกอกมีสารโพลีฟีนอล (Polyphenols) ซึ่งเป็นสารต้านอนุมูลอิสระที่ให้รสชาติและกลิ่นหอม แต่เมื่อเวลาผ่านไป สารเหล่านี้จะลดลง ทำให้น้ำมันเสียรสชาติ
- ระดับความเป็นกรด (Acidity Level) ตัวนี้หละที่ผมโคตรเน้น และพูดบ่อยมาก จนหลายๆคนเบื่อ 5555 น้ำมันมะกอก Extra Virgin ต้องมี ค่าความเป็นกรดต่ำกว่า 0.8% ค่ายิ่งต่ำ ยิ่งดี เพราะหมายความว่ามะกอกถูกเก็บเกี่ยวอย่างเหมาะสมและสกัดอย่างรวดเร็ว
- ระดับความเข้มของรสชาติ เรื่องการกินก็สำคัญนะครับน้ำมันมะกอกมีระดับความเข้มต่างกัน ควรเลือกให้เหมาะกับอาหาร รสอ่อน (Delicate) เหมาะกับปลา เนื้อขาว และสลัดเบาๆ ,รสปานกลาง (Moderate) เหมาะกับพาสต้า ผักย่าง และชีส รสเข้มข้น (Intense) เหมาะกับเนื้อแดง ช็อกโกแลต และอาหารที่มีรสจัด
ส่วนตราที่บอกไว้ข้างบนโน้นนน จำไว้เลยว่า อย่าหลงเชื่อคำว่า "Organic" เพียงอย่างเดียว เพราะการปลูกแบบออร์แกนิกไม่ได้รับประกันว่ารสชาติจะดีเสมอไป หลีกเลี่ยงน้ำมันมะกอกที่ระบุว่า "Product of EU" เพราะอาจเป็นการผสมจากหลายประเทศ
สำหรับเรื่องฉลากนะครับ ใครที่ดื่มไวน์โลกเก่าจะคุ้นเคยความที่ต้องอ่านรายละเอียดพวกนี้เป็นอย่างดี น้ำมันมะกอกแบบ extra virgin olive oil ที่ดี ฉลากและแพคเกจจะต้องมีประมาณนี้ครับ 1.ระดับกรดอิสระ (Free Fatty Acids, FFA) หรือ กรดโอเลอิก (%) ต้องไม่เกิน 0.8% ตามมาตรฐานของ International Olive Council (IOC) ถ้าค่าตัวนี้ยิ่งต่ำ แสดงว่าน้ำมันมะกอกมีคุณภาพดีขึ้น เพราะบ่งบอกว่าผลมะกอกถูกสกัดอย่างดี ไม่ผ่านกระบวนการที่ทำให้เสื่อมสภาพ 2. ค่าความเป็นออกซิเดชัน (Peroxide Value, PV) (meq O₂/kg) ต้องไม่เกิน 20 meq O₂/kg คือไม่ต้องรู้ก็ได้ครับว่ามาจากไหน เอาว่าถ้าค่าสูงเกินไป แสดงว่าน้ำมันเริ่มเหม็นหืนจากปฏิกิริยาออกซิเดชัน 3. ค่า K232 และ K270 (UV Absorbance at 232 nm และ 270 nm) โดยที่ K232 ต้องไม่เกิน 2.50 (บ่งบอกถึงการเกิดออกซิเดชันระยะแรก) และ K270 ต้องไม่เกิน 0.22 (บ่งบอกถึงการเสื่อมสภาพของน้ำมัน) ค่าเหล่านี้ใช้แสง UV ตรวจจับว่ามีการกลั่นน้ำมันอื่นผสมเข้ามาหรือไม่ 4. ค่า Delta-K (ΔK) ต้องไม่เกิน 0.01 ค่านี้ใช้ตรวจจับว่าน้ำมันมีการปนเปื้อนหรือถูกดัดแปลงด้วยสารอื่นไหม 5. ประเทศต้นกำเนิด (Country of Origin) น้ำมันมะกอกที่มีคุณภาพดีมักระบุชื่อฟาร์มหรือแหล่งผลิตที่ชัดเจน เช่น อิตาลี สเปน กรีซ 6. วันที่เก็บเกี่ยว (Harvest Date) และวันหมดอายุ (Best Before Date) ควรเลือกน้ำมันที่มีวันที่เก็บเกี่ยวล่าสุด (อายุการเก็บรักษาโดยทั่วไปคือ 18-24 เดือน) 7. วิธีการสกัด (Extraction Method) ต้องระบุว่าเป็น "Cold Pressed" หรือ "Cold Extracted" หมายถึงสกัดโดยไม่ใช้ความร้อน ซึ่งช่วยรักษาคุณภาพของสารอาหาร 8. ปริมาณโพลีฟีนอล (Polyphenol Content) (mg/kg) [อาจไม่มีในทุกยี่ห้อ] น้ำมันมะกอกคุณภาพสูงมักมีโพลีฟีนอลมากกว่า 250 mg/kg ซึ่งช่วยลดการอักเสบในร่างกาย แต่บางยี่ห้อก็จะให้ดูที่วิตามิน E กับ K เพราะ น้ำมันมะกอกที่มี Polyphenol สูงมักจะมีปริมาณ วิตามิน E ที่สูงตามไปด้วย และการที่น้ำมันมะกอกมี วิตามิน K ก็อาจสะท้อนถึงการที่น้ำมันมะกอกนั้นไม่ได้ถูกผ่านกระบวนการปรับแต่งหรือแปรรูปที่มากจนเกินไป ทำให้รักษาสารอาหารที่สำคัญ รวมถึง Polyphenol ไว้ได้ 9. บรรจุภัณฑ์ ควรเป็นขวดแก้วสีเข้มหรือกระป๋องโลหะ เพื่อป้องกันการเสื่อมสภาพจากแสง
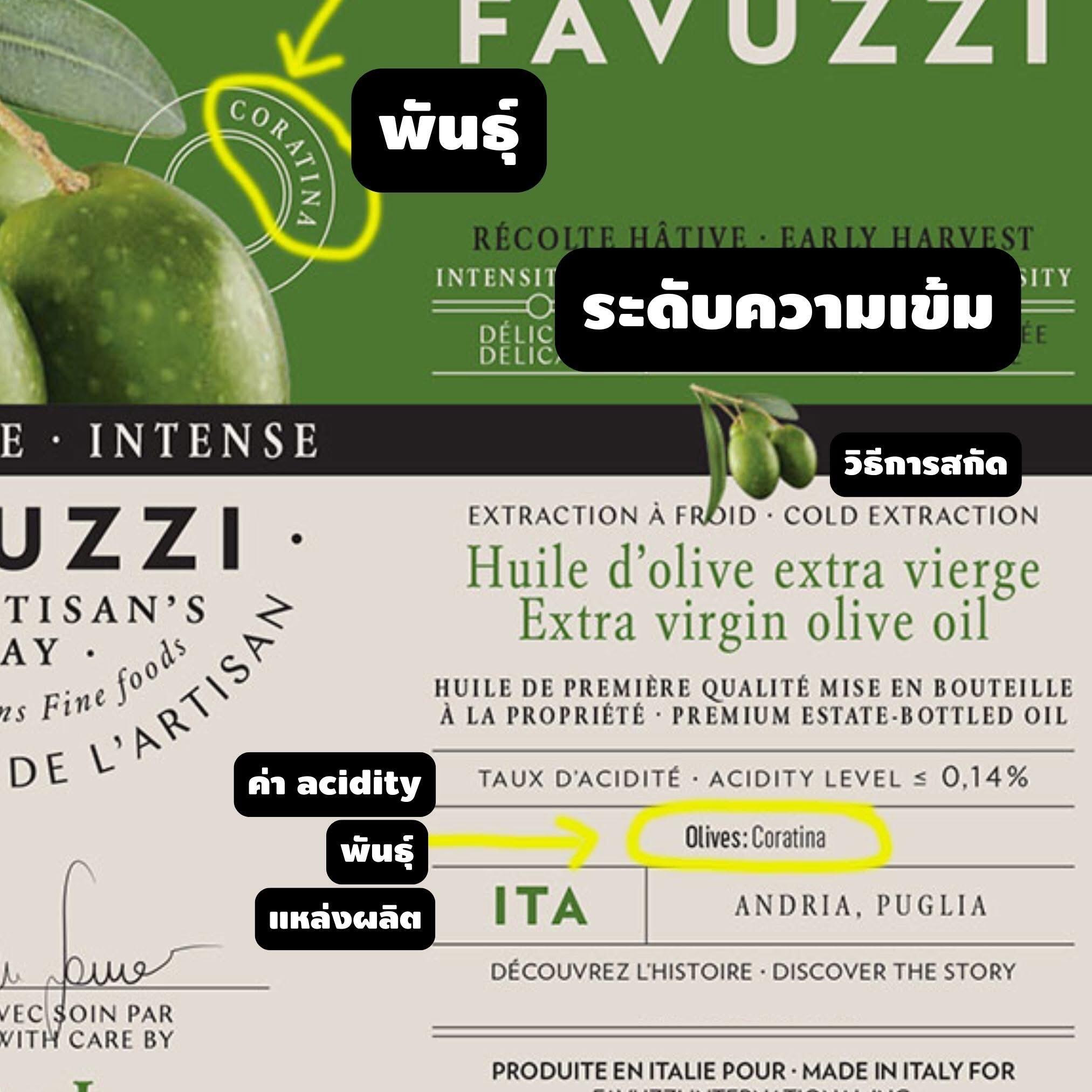
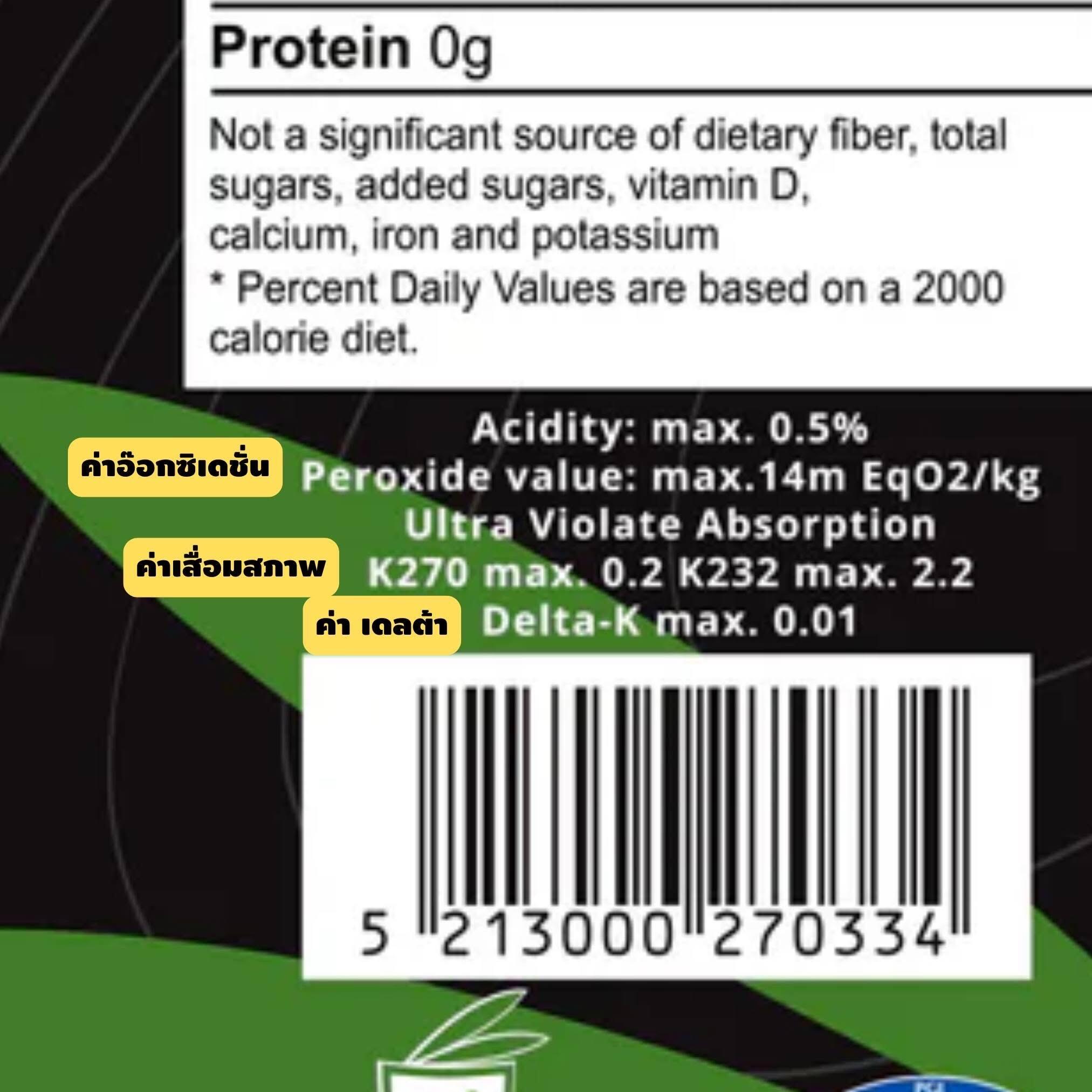
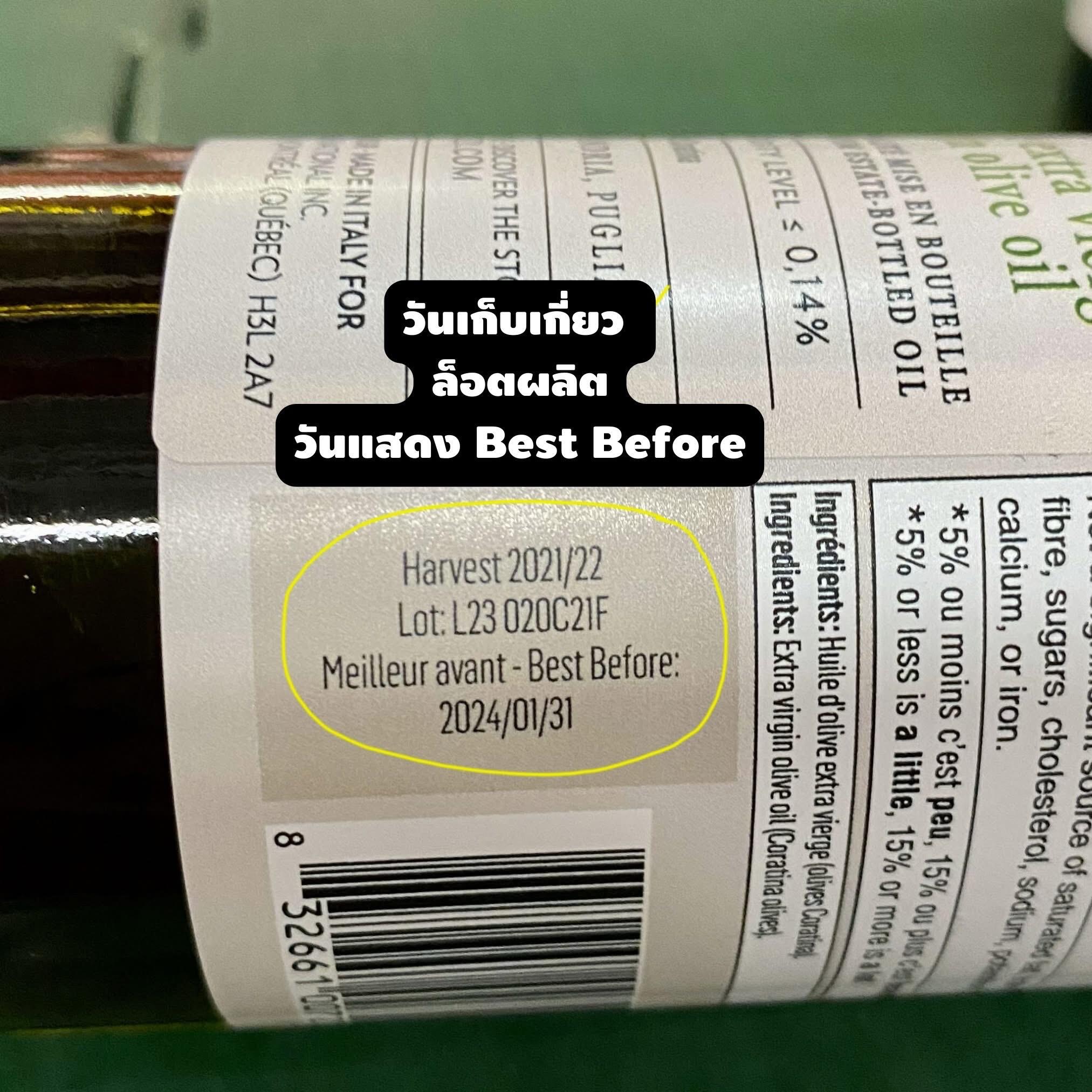
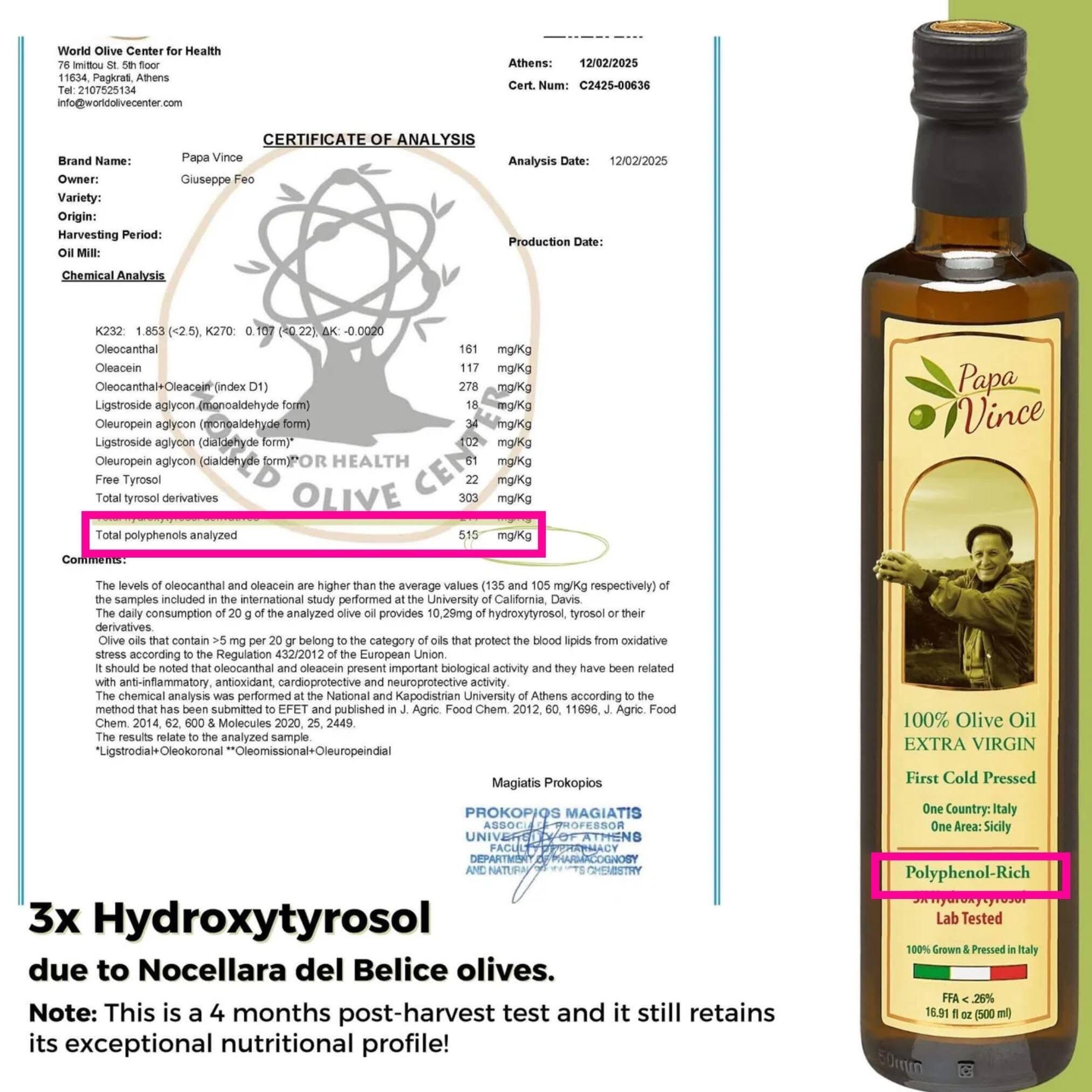
ใน 9 ข้อนี้ ไม่จำเป็นต้องมีครบทุกข้อก็ได้นะครับ เท่าที่ผมพยายามหาในไทย เจอ acidity ก็บุญโขแล้วครับ 55555 บางทีเขาก็อาจไม่ได้แปะไว้บนฉลาก แต่ต้องตามไปอ่านในเว็บของผู้ผลิตก็ได้ครับ
ส่วนใครที่อ่านถึงตรงนี้แล้วท้อใจ ไม่อยากกินมันแล้ว ก็ขอบอกว่า โลกมันก็เป็นแบบนี้แหละครับ ของมันมีราคามากจนต้องมีการปลอมกัน มันไม่ได้โหดร้ายขนาดนั้นหรอกครับ กระเป๋าแบรนด์เนมก็ปลอมกันเกลื่อน นาฬิกาก็ปลอมกันทั่ว แต่คุณๆก็มองออกใช่ไหมครับ น้ำมันมะกอกมันก็ไม่ต่างกันหรอกครับ มันคือเรื่องที่ไม่ธรรมดาของโลกนี้ที่คนทำเป็นเรื่องธรรมดา
ถ้ามันดูหดหู่ไป จำง่ายๆก็ได้ครับว่า "ทุกน้ำมันมะกอกปลอม จะไม่มีฉลากที่บอกรายละเอียดดีๆ แต่ ทุกน้ำมันมะกอกที่ไม่มีฉลากรายละเอียดดีๆ ไม่ได้เป็นน้ำมันมะกอกปลอม" logic แบบง่ายๆนี้เลยครับ
ผมได้แค่บอกว่า สิ่งที่ควรดูเพื่อแลกกับเงินที่ต้องจ่ายให้มันมากๆคืออะไร แล้วสิ่งที่เราจ่ายไปบริโภค เราได้แบบนั้นจริงๆไหม อย่างที่เคยบอกใน #ฉลาก3รู้ เสมอๆคือ ฉลากไม่ได้เป็นตัวประกาศิตที่จะบอกว่าใครไม่มีคือแย่ แต่ฉลากมันเหมือนคำมันสัญญา ว่าผู้ผลิตจะทำตามที่เขียนเอาไว้ ถ้าใครที่กล้าบิดพริ้วจากนั้น หรือ ทำไม่จริงตามฉลาก มันก็คือการที่เขากล้าทำผิดสัญญา และมันต้องแลกมาด้วยค่าใช้จ่าย ไม่ว่าจะชื่อเสียง ความน่าเชื่อถือ หรือ ความภาคภูมิใจ เราคงทำอะไรไม่ได้มากกว่านั้น จะใช้กระบวนการ ก็ต้องพิสูจน์ ใช้เวลา เพราะที่เห็นในบ้านเราก็มีตัวอย่างมากมาย แต่มันก็ "อย่างน้อย" มันวัดกันหล่ะวะ ว่า แกกล้าสัญญากับชั้นมั๊ย
โอเคมะ ถ้าคุณจะหนี มันต้องหนีตลอดไปในทุกๆอย่างครับ หรือจะให้ผมเล่าเรื่อง fun fact ของกินเทพอื่นๆ ที่พวกคุณกินกันอย่างเป็นล่ำเป็นสันเพื่อกระตุ้นให้ศึกษาเพิ่มไหมหล่ะ 55555
#pirateketo #ฉลาก3รู้ #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ a3a17f65:e9606ad9
2025-03-25 02:22:32
@ a3a17f65:e9606ad9
2025-03-25 02:22:32Maybe it’s the novelty, or perhaps a placebo effect. Maybe it's the sense of finally accomplishing something I’ve set out to do a long time ago. But the first impression is that writing has already begun to clear my mind. It seems to be one of the most powerful ways to improve thinking. Developing the habit of writing could lead to becoming a better thinker.
This journal is meant to reflect whatever’s on my mind. But posting it online comes with a different set of pros and cons compared to what most productivity gurus recommend. For instance, I’ll cut out personal thoughts or sensitive information—something essential in a personal journal. I could mitigate such flaw by writing two versions: one for public view and one for myself, but that feels like too much hassle when I’m just starting this new habit (as James Clear advises, make your habits easy!). On the flip side, posting on cyberspace forces me to be mindful of you, dear reader. Writing for myself alone would allow me to leave empty spaces between familiar ideas and have no problem joining the dots later. But here, fortunately, that luxury doesn’t exist.
Another complementary habit that’s been nagging at me lately is reading, especially fiction—not for learning, but for the pure joy of reading without the pressure to take notes or analyze everything. I just came across this post and despite not being plagued by the obsessive use of smart phones and social media, these two phrases caught my eye:
Reading literary fiction has been linked to having more empathy and the ability to engage in critical thinking
I’ve always valued critical thinking, so that didn’t surprise me. But the link to empathy caught my attention. It made me think about how reading fiction let us experience different perspectives, possibly engaging the same mirror-neurons activated during real-life interactions. Fascinating how something that sharpens our minds can also help us connect with others on a deeper level.
I feel like myself again. Did I mention I’m also sleeping better, and feel happier too?
This quote resonated on a deep level. For me, a single day of writing has given me a most welcomed sense of accomplishment due to being true to myself. Combining journaling with joyful reading might be one of the most powerful boosts to both sleep quality and a sense of purpose I’ve experienced in a long time.
-
 @ 1d7ff02a:d042b5be
2025-03-25 02:01:41
@ 1d7ff02a:d042b5be
2025-03-25 02:01:41ໃນຍຸກດິຈິຕອນ, ການລົບກວນທາງເທັກໂນໂລຊີໄດ້ສັ່ນຄອນສະຖາບັນແບບດັ້ງເດີມທົ່ວໂລກ. ເຊັ່ນດຽວກັນກັບແພລດຟອມສື່ສັງຄົມອອນລາຍທີ່ໄດ້ທຳລາຍອິດທິພົນຂອງສື່ທ້ອງຖິ່ນ, Tether (USDT) ແລະ ສະເຕເບິນຄອຍອື່ນໆ ກຳລັງທ້າທາຍອຳນາດຂອງທະນາຄານກາງໃນປະເທດກຳລັງພັດທະນາ. ສະກຸນເງິນດິຈິຕອນທີ່ມີຄວາມສະຖຽນເຫຼົ່ານີ້ ສະເໜີວິທີການສຳລັບປະຊາຊົນເພື່ອປ້ອງກັນເງິນເຟີ້, ຫຼີກລ່ຽງການຄວບຄຸມທຶນ, ແລະ ເຂົ້າເຖິງຕະຫຼາດການເງິນໂລກໂດຍບໍ່ຕ້ອງອີງໃສ່ລະບົບທະນາຄານແບບດັ້ງເດີມ. ໃນຂະນະທີ່ການນຳໃຊ້ກຳລັງເພີ່ມຂຶ້ນ, USDT ກຳລັງກາຍເປັນໄພຂົ່ມຂູ່ທີ່ມີຢູ່ຈິງຕໍ່ທະນາຄານກາງ, ຈຳກັດການຄວບຄຸມຂອງພວກເຂົາຕໍ່ນະໂຍບາຍການເງິນ ແລະ ອຳນາດອະທິປະໄຕທາງການເງິນ.
ທາງເລືອກໃໝ່ແທນສະກຸນເງິນທ້ອງຖິ່ນ
ປະເທດກຳລັງພັດທະນາມັກຈະປະສົບບັນຫາກັບການລົດຄ່າເງິນ, ເງິນເຟີ້, ແລະ ການໄຫລອອກຂອງທຶນ. ທະນາຄານກາງຫຼາຍແຫ່ງບໍ່ສາມາດຮັກສາສະຖຽນລະພາບຂອງສະກຸນເງິນເນື່ອງຈາກການຄຸ້ມຄອງທີ່ບໍ່ດີ, ການພິມເງິນຫຼາຍເກີນໄປ, ຫຼື ການແຊກແຊງທາງການເມືອງ. ພົນລະເມືອງທີ່ເຫັນເງິນທ້ອນຂອງຕົນຖືກກັດເຊາະ ຕາມປົກກະຕິແລ້ວຈະມີທາງເລືອກບໍ່ຫຼາຍ: ປ່ຽນເງິນທ້ອງຖິ່ນເປັນ ໂດລາ ຫລື ໃນກໍລະນີ້ລາວເຮົາກໍຈະມີ ບາດ ແລະ ຢວນນຳ ຜ່ານທະຫລາດມືດ ຫຼື ລົງທຶນກັບທຸລະກິດ, ຊື້ອະສັງຫາ ແລະ ລົງທຶນໃນຊັບສິນຕ່າງປະເທດ. USDT ໄດ້ປ່ຽນແປງເກມນີ້. ມັນອະນຸຍາດໃຫ້ທຸກຄົນທີ່ມີການເຂົ້າເຖິງອິນເຕີເນັດສາມາດເກັບຮັກສາ ແລະ ໂອນມູນຄ່າໃນຮູບແບບດິຈິຕອນທີ່ທຽບເທົ່າກັບໂດລາໂດຍບໍ່ຈຳເປັນຕ້ອງໄດ້ຮັບການອະນຸມັດຈາກທະນາຄານທ້ອງຖິ່ນ ຫຼື ລັດຖະບານ. ສິ່ງນີ້ຊ່ວຍໃຫ້ຫຼຸດພົ້ນຈາກການອີງໃສ່ສະກຸນເງິນແຫ່ງຊາດທີ່ອ່ອນແອ, ສະເໜີທາງເລືອກທີ່ງ່າຍໃນການປ້ອງກັນການເສື່ອມຄ່າ. ໃນປະເທດເຊັ່ນ: ເວເນຊູເອລາ, ອາເຈນຕິນາ, ໄນຈີເຣຍ, ເລບານອນ, ແລະ ລາວ, ປະຊາຊົນກຳລັງນຳໃຊ້ USDT ເພື່ອປົກປ້ອງຄວາມໝັ້ງຄັ່ງຂອງພວກເຂົາຈາກພາວະເງິນເຟີ້ສູງ ແລະ ຄວາມບໍ່ສະຖຽນທາງການເງິນ.
ການທຳລາຍການຜູກຂາດຂອງທະນາຄານກາງ
ທະນາຄານກາງມີອຳນາດອັນໃຫຍ່ຫຼວງຕໍ່ລະບົບການເງິນໂດຍການຄວບຄຸມການອອກເງິນ, ອັດຕາດອກເບ້ຍ, ແລະ ການໄຫຼຂອງທຶນ. ເຖິງຢ່າງໃດກໍຕາມ, USDT ບ່ອນທຳລາຍການຄວບຄຸມນີ້ດ້ວຍການສະໜອງລະບົບການເງິນຄູ່ຂະໜານທີ່ດຳເນີນງານເປັນອິດສະຫຼະຈາກການກຳກັບດູແລຂອງລັດຖະບານ. ສິ່ງນີ້ທ້າທາຍສາມພື້ນທີ່ຫຼັກຂອງອຳນາດທະນາຄານກາງ:
- ການຄວບຄຸມນະໂຍບາຍການເງິນ:
ເມື່ອປະຊາຊົນຍ້າຍເງິນທ້ອນຈາກສະກຸນເງິນທ້ອງຖິ່ນໄປສູ່ USDT, ທະນາຄານກາງຈະສູນເສຍຄວາມສາມາດໃນການຄວບຄຸມປະລິມານເງິນຢ່າງມີປະສິດທິພາບ. ຖ້າປະຊາກອນສ່ວນໃຫຍ່ຢຸດໃຊ້ສະກຸນເງິນແຫ່ງຊາດ, ນະໂຍບາຍເຊັ່ນ: ການປ່ຽນແປງອັດຕາດອກເບ້ຍ ຫຼື ການພິມເງິນກໍຈະສູນເສຍປະສິດທິພາບຂອງພວກມັນ.
- ການຫຼີກລ່ຽງການຄວບຄຸມທຶນ:
ປະເທດກຳລັງພັດທະນາຫຼາຍແຫ່ງບັງຄັບໃຊ້ການຄວບຄຸມທຶນທີ່ເຂັ້ມງວດເພື່ອປ້ອງກັນບໍ່ໃຫ້ເງິນອອກນອກປະເທດ, ເຮັດໃຫ້ສະກຸນເງິນຂອງພວກເຂົາມີສະຖຽນລະພາບ. USDT, ໂດຍບໍ່ມີພົມແດນ, ອະນຸຍາດໃຫ້ຜູ້ໃຊ້ຫຼີກລ່ຽງການຄວບຄຸມເຫຼົ່ານີ້, ເຮັດໃຫ້ມັນງ່າຍຂຶ້ນໃນການດຳເນີນທຸລະກຳທົ່ວໂລກ ຫຼື ເກັບຮັກສາຄວາມໝັ້ງຄັ່ງທີ່ມີສະພາບຄ່ອງລະດັບສາກົນ.
- ການລົດບົດບາດຂອງລະບົບທະນາຄານ:
USDT ຫຼຸດຄວາມຕ້ອງການຂອງການບໍລິການທະນາຄານແບບດັ້ງເດີມ. ດ້ວຍສະມາດໂຟນ ແລະ ກະເປົາເງິນດິຈິຕອນ, ປະຊາຊົນສາມາດສົ່ງ ແລະ ຮັບການຊຳລະເງິນໂດຍບໍ່ຕ້ອງຜ່ານລະບົບທະນາຄານ, ຕັດທະນາຄານອອກຈາກລະບົບນິເວດການເງິນ ແລະ ເຮັດໃຫ້ພວກມັນຂາດຄ່າທຳນຽມທຸລະກຳ ແລະ ເງິນຝາກ.
ກໍລະນີຂອງລາວ: ການປ່ຽນແປງທາງການເງິນທີ່ກຳລັງເກີດຂຶ້ນ
ລາວ, ເຊັ່ນດຽວກັນກັບປະເທດກຳລັງພັດທະນາຫຼາຍແຫ່ງ, ປະເຊີນກັບສິ່ງທ້າທາຍທາງເສດຖະກິດລວມທັງເງິນເຟີ້, ສະກຸນເງິນແຫ່ງຊາດທີ່ອ່ອນແອ (ເງິນກີບລາວ), ແລະ ການເຂົ້າເຖິງເງິນຕາຕ່າງປະເທດທີ່ຈຳກັດ. ລັດຖະບານມີການຄວບຄຸມທຶນທີ່ເຂັ້ມງວດ, ເຮັດໃຫ້ມັນຍາກສຳລັບບຸກຄົນ ແລະ ທຸລະກິດໃນການຊື້ USD ຜ່ານຊ່ອງທາງທີ່ເປັນທາງການ. ສິ່ງນີ້ເຮັດໃຫ້ເກີດຕະຫຼາດມືດສຳລັບການແລກປ່ຽນເງິນຕາທີ່ເຕີບໂຕຂຶ້ນ. ດ້ວຍການເພີ່ມຂຶ້ນຂອງ USDT, ຊາວລາວຫຼາຍຄົນກຳລັງຫັນມາໃຊ້ stable coin ແລະ ເກັບຊັບສິນດິຈິຕອນ ເປັນທາງເລືອກທີ່ປອດໄພກວ່າການຖືເງິນກີບລາວ, ເຊິ່ງມີແນວໂນ້ມທີ່ຈະເສື່ອມຄ່າລົງ.
ບົດຮຽນຈາກການທຳລາຍສື່ທ້ອງຖິ່ນໂດຍສື່ສັງຄົມອອນລາຍ
ການເພີ່ມຂຶ້ນຂອງ USDT ສະທ້ອນໃຫ້ເຫັນເຖິງສື່ສັງຄົມອອນລາຍໄດ້ທຳລາຍສື່ທ້ອງຖິ່ນແນວໃດ. ສື່ຂ່າວແບບດັ້ງເດີມເຄີຍຜູກຂາດການແຈກຢາຍຂໍ້ມູນ, ແຕ່ແພລດຟອມເຊັ່ນ: Facebook, Twitter, ແລະ YouTube ໄດ້ເຮັດໃຫ້ການສ້າງ ແລະ ການແຈກຢາຍເນື້ອຫາເປັນປະຊາທິປະໄຕ. ດັ່ງນັ້ນ, ສື່ທີ່ຄວບຄຸມໂດຍລັດ ແລະ ບໍລິສັດຈຶ່ງສູນເສຍຄວາມສາມາດໃນການກຳນົດເນື້ອຫາ ໃນຂະນະທີ່ສື່ສັງຄົມອອນລາຍເພີ່ມອຳນາດໃຫ້ບຸກຄົນໃນການແບ່ງປັນ ແລະ ເຂົ້າເຖິງຂ່າວທີ່ບໍ່ໄດ້ຜ່ານການ censorship. ເຊັ່ນດຽວກັນ, USDT ກຳລັງກະຈາຍອຳນາດທາງການເງິນ. ເຊັ່ນດຽວກັບສື່ສັງຄົມອອນລາຍທີ່ໃຫ້ສຽງແກ່ປະຊາຊົນນອກເໜືອຈາກສື່ກະແສຫຼັກ, USDT ກຳລັງໃຫ້ຄວາມເປັນອິດສະຫຼະທາງການເງິນແກ່ບຸກຄົນທີ່ເກີນກວ່າຂອບເຂດຂອງທະນາຄານກາງ. ແນວໂນ້ມນີ້ຊັດເຈນ: ສະຖາບັນທີ່ລວມສູນຈະສູນເສຍການຄວບຄຸມເມື່ອບຸກຄົນໄດ້ຮັບການເຂົ້າເຖິງໂດຍກົງຕໍ່ທາງເລືອກອື່ນ.
Trump ສະໜັບສະໜູນ Stable Coin
ປະທານາທິບໍດີສະຫະລັດ Donald Trump ໄດ້ສະແດງການສະໜັບສະໜູນຕໍ່ stable coin ແລະ ອຸດສາຫະກຳ cryptocurrency ເມື່ອບໍ່ດົນມານີ້. ຈຸດຢືນຂອງລາວເປັນສັນຍານເຖິງການປ່ຽນແປງທີ່ເປັນໄປໄດ້ໃນນະໂຍບາຍຂອງສະຫະລັດທີ່ອາດຈະສ້າງຄວາມຊອບທຳໃຫ້ແກ່ສະເຕເບິນຄອຍ ແລະ ຂັບເຄື່ອນການນຳໃຊ້ທົ່ວໂລກ. ຖ້າລັດຖະບານສະຫະລັດຮັບຮອງສະເຕເບິນຄອຍເຊັ່ນ USDT, ມັນອາດຈະເລັ່ງການນຳໃຊ້ພວກມັນເປັນທາງເລືອກແທນລະບົບທະນາຄານແບບດັ້ງເດີມ, ສ້າງແຮງກົດດັນເພີ່ມເຕີມຕໍ່ທະນາຄານກາງໃນປະເທດກຳລັງພັດທະນາ. ນີ້ອາດຈະສົ່ງເສີມໃຫ້ມີການມີສ່ວນຮ່ວມຂອງສະຖາບັນຫຼາຍຂຶ້ນ, ເຮັດໃຫ້ມັນຍາກຂຶ້ນສຳລັບລັດຖະບານທ້ອງຖິ່ນໃນການປາບປາມການນຳໃຊ້ USDT.
ຊ່ອງຫວ່າງຂອງການຮັບຮູ້: ຫຼາຍຄົນຍັງບໍ່ຮູ້ເຖິງໄພຂົ່ມຂູ່
ເຖິງແມ່ນວ່າ USDT ຈະເຕີບໂຕຢ່າງໄວວາ, ປະຊາຊົນຫຼາຍຄົນໃນປະເທດກຳລັງພັດທະນາຍັງບໍ່ຮັບຮູ້ເຖິງຜົນກະທົບຂອງມັນ. ໃນຂະນະທີ່ຜູ້ໃຊ້ເລີ່ມຕົ້ນຈະເປັນ ບຸກຄົນທີ່ຮູ້ເທັກໂນໂລຊີ, ນັກລົງທຶນ ແລະ ເຈົ້າຂອງທຸລະກິດ, ປະຊາກອນສ່ວນໃຫຍ່ຍັງອີງໃສ່ການທະນາຄານແບບດັ້ງເດີມ ແລະ ສະກຸນເງິນຕາມກົດໝາຍໂດຍບໍ່ຮູ້ເຖິງຄວາມສ່ຽງຂອງການເສື່ອມຄ່າ ແລະ ຄວາມບໍ່ສະຖຽນທາງການເງິນ. ເຖິງຢ່າງໃດກໍຕາມ, ບຸກຄົນຕ້ອງມີຄວາມຄິດລິເລີ່ມໃນການສຶກສາຕົນເອງກ່ຽວກັບເຄື່ອງມືທາງການເງິນທາງເລືອກເຊັ່ນ USDT ແລະ Bitcoin ເພື່ອປົກປ້ອງຄວາມໝັ້ງຄັ່ງ ແລະ ຄວາມເປັນອິດສະຫຼະທາງການເງິນຂອງພວກເຂົາ.
ບົດສະຫຼຸບ: ການປະຕິວັດທາງການເງິນທີ່ກຳລັງເກີດຂຶ້ນ
USDT ແລະ Bitcoin ແມ່ນການປະຕິວັດທາງການເງິນທີ່ເພີ່ມອຳນາດໃຫ້ບຸກຄົນໃນປະເທດກຳລັງພັດທະນາທີ່ຈະຫຼຸດພົ້ນຈາກນະໂຍບາຍການເງິນທີ່ລົ້ມເຫຼວ. ເຊັ່ນດຽວກັບສື່ສັງຄົມອອນລາຍໄດ້ປະຕິວັດພູມທັດຂອງສື່ໂດຍການໃຫ້ປະຊາຊົນຄວບຄຸມຂໍ້ມູນຂ່າວສານ, USDT ກຳລັງປະຕິວັດການເງິນໂດຍການໃຫ້ປະຊາຊົນຄວບຄຸມເງິນຂອງພວກເຂົາ. ສຳລັບທະນາຄານກາງໃນປະເທດກຳລັງພັດທະນາ, ການປ່ຽນແປງນີ້ສ້າງສະພາວະຫຍຸ້ງຍາກທີ່ຮ້າຍແຮງ: ປັບຕົວ ຫຼື ສູນເສຍອິດທິພົນ. ລັດຖະບານອາດຈະພະຍາຍາມຄວບຄຸມກົດລະບຽບ ຫຼື ຫ້າມສະເຕເບິນຄອຍ, ແຕ່ຕາມທີ່ປະຫວັດສາດໄດ້ສະແດງໃຫ້ເຫັນກັບສື່ສັງຄົມອອນລາຍ.
-
 @ 98028d3f:24448238
2025-03-25 01:57:54
@ 98028d3f:24448238
2025-03-25 01:57:54我写这个例子主要看如何更新修改的1。
-
 @ 21335073:a244b1ad
2025-03-18 14:43:08
@ 21335073:a244b1ad
2025-03-18 14:43:08Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ fd06f542:8d6d54cd
2025-03-25 01:40:53
@ fd06f542:8d6d54cd
2025-03-25 01:40:5330023的 文章 可发以被 删除 1 吗?
-
 @ da0b9bc3:4e30a4a9
2025-03-24 22:50:57
@ da0b9bc3:4e30a4a9
2025-03-24 22:50:57Hello Stackers!
It's Monday so we're back doing "Meta Music Mondays" 😉.
From before the territory existed there was just one post a week in a ~meta take over. Now each month we have a different theme and bring music from that theme.
This month is March and we're doing March Madness. So give me those Wacky and Weird crazy artists and songs. The weirder the better!
Let's have fun.
Can't have March Madness without Madness!
https://youtu.be/SOJSM46nWwo?si=gtghOZte3rh41tXg
Talk Music. Share Tracks. Zap Sats.
originally posted at https://stacker.news/items/924076
-
 @ 6e0ea5d6:0327f353
2025-03-24 22:42:59
@ 6e0ea5d6:0327f353
2025-03-24 22:42:59🎣
The support I never had could have saved me time, and I would certainly be farther along at this moment. However, that absence taught me to value having, and if I pass this lesson on to you earlier, it is so you have more time to learn what I could not see.
I like what my father once paraphrased: "If I have seen further, it is by standing on the shoulders of giants." And right now, I think of all that the little one who descends from you will one day behold. The heaviest burdens I pushed were so that you could soar, and if I have dedicated my existence to you, it is so that from my ashes, you may always rise again.
Out of love, I will try not to spoil you with excessive gifts, but instead, without being absent, I hope to build you up. With this line and these strands, I wish to teach you to catch your own fish. Live by what I have taught you and seek to understand what I could not. Honor who I was for you by becoming the best you can be.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 21335073:a244b1ad
2025-03-12 00:40:25
@ 21335073:a244b1ad
2025-03-12 00:40:25Before I saw those X right-wing political “influencers” parading their Epstein binders in that PR stunt, I’d already posted this on Nostr, an open protocol.
“Today, the world’s attention will likely fixate on Epstein, governmental failures in addressing horrific abuse cases, and the influential figures who perpetrate such acts—yet few will center the victims and survivors in the conversation. The survivors of Epstein went to law enforcement and very little happened. The survivors tried to speak to the corporate press and the corporate press knowingly covered for him. In situations like these social media can serve as one of the only ways for a survivor’s voice to be heard.
It’s becoming increasingly evident that the line between centralized corporate social media and the state is razor-thin, if it exists at all. Time and again, the state shields powerful abusers when it’s politically expedient to do so. In this climate, a survivor attempting to expose someone like Epstein on a corporate tech platform faces an uphill battle—there’s no assurance their voice would even break through. Their story wouldn’t truly belong to them; it’d be at the mercy of the platform, subject to deletion at a whim. Nostr, though, offers a lifeline—a censorship-resistant space where survivors can share their truths, no matter how untouchable the abuser might seem. A survivor could remain anonymous here if they took enough steps.
Nostr holds real promise for amplifying survivor voices. And if you’re here daily, tossing out memes, take heart: you’re helping build a foundation for those who desperately need to be heard.“
That post is untouchable—no CEO, company, employee, or government can delete it. Even if I wanted to, I couldn’t take it down myself. The post will outlive me on the protocol.
The cozy alliance between the state and corporate social media hit me hard during that right-wing X “influencer” PR stunt. Elon owns X. Elon’s a special government employee. X pays those influencers to post. We don’t know who else pays them to post. Those influencers are spurred on by both the government and X to manage the Epstein case narrative. It wasn’t survivors standing there, grinning for photos—it was paid influencers, gatekeepers orchestrating yet another chance to re-exploit the already exploited.
The bond between the state and corporate social media is tight. If the other Epsteins out there are ever to be unmasked, I wouldn’t bet on a survivor’s story staying safe with a corporate tech platform, the government, any social media influencer, or mainstream journalist. Right now, only a protocol can hand survivors the power to truly own their narrative.
I don’t have anything against Elon—I’ve actually been a big supporter. I’m just stating it as I see it. X isn’t censorship resistant and they have an algorithm that they choose not the user. Corporate tech platforms like X can be a better fit for some survivors. X has safety tools and content moderation, making it a solid option for certain individuals. Grok can be a big help for survivors looking for resources or support! As a survivor, you know what works best for you, and safety should always come first—keep that front and center.
That said, a protocol is a game-changer for cases where the powerful are likely to censor. During China's # MeToo movement, survivors faced heavy censorship on social media platforms like Weibo and WeChat, where posts about sexual harassment were quickly removed, and hashtags like # MeToo or "woyeshi" were blocked by government and platform filters. To bypass this, activists turned to blockchain technology encoding their stories—like Yue Xin’s open letter about a Peking University case—into transaction metadata. This made the information tamper-proof and publicly accessible, resisting censorship since blockchain data can’t be easily altered or deleted.
I posted this on X 2/28/25. I wanted to try my first long post on a nostr client. The Epstein cover up is ongoing so it’s still relevant, unfortunately.
If you are a survivor or loved one who is reading this and needs support please reach out to: National Sexual Assault Hotline 24/7 https://rainn.org/
Hours: Available 24 hours
-
 @ 0c469779:4b21d8b0
2025-03-11 10:52:49
@ 0c469779:4b21d8b0
2025-03-11 10:52:49Sobre el amor
Mi percepción del amor cambió con el tiempo. Leer literatura rusa, principalmente a Dostoevsky, te cambia la perspectiva sobre el amor y la vida en general.
Por mucho tiempo mi visión sobre la vida es que la misma se basa en el sufrimiento: también la Biblia dice esto. El amor es igual, en el amor se sufre y se banca a la otra persona. El problema es que hay una distinción de sufrimientos que por mucho tiempo no tuve en cuenta. Está el sufrimiento del sacrificio y el sufrimiento masoquista. Para mí eran indistintos.
Para mí el ideal era Aliosha y Natasha de Humillados y Ofendidos: estar con alguien que me amase tanto como Natasha a Aliosha, un amor inclusive autodestructivo para Natasha, pero real. Tiene algo de épico, inalcanzable. Un sufrimiento extremo, redentor, es una vara altísima que en la vida cotidiana no se manifiesta. O el amor de Sonia a Raskolnikov, quien se fue hasta Siberia mientras estuvo en prisión para que no se quede solo en Crimen y Castigo.
Este es el tipo de amor que yo esperaba. Y como no me pasó nada tan extremo y las situaciones que llegan a ocurrir en mi vida están lejos de ser tan extremas, me parecía hasta poco lo que estaba pidiendo y que nadie pueda quedarse conmigo me parecía insuficiente.
Ahora pienso que el amor no tiene por qué ser así. Es un pensamiento nuevo que todavía estoy construyendo, y me di cuenta cuando fui a la iglesia, a pesar de que no soy cristiano. La filosofía cristiana me gusta. Va conmigo. Tiene un enfoque de humildad, superación y comunidad que me recuerda al estoicismo.
El amor se trata de resaltar lo mejor que hay en el otro. Se trata de ser un plus, de ayudar. Por eso si uno no está en su mejor etapa, si no se está cómodo con uno mismo, no se puede amar de verdad. El amor empieza en uno mismo.
Los libros son un espejo, no necesariamente vas a aprender de ellos, sino que te muestran quién sos. Resaltás lo que te importa. Por eso a pesar de saber los tipos de amores que hay en los trabajos de Dostoevsky, cometí los mismos errores varias veces.
Ser mejor depende de uno mismo y cada día se pone el granito de arena.
-
 @ 4857600b:30b502f4
2025-03-10 12:09:35
@ 4857600b:30b502f4
2025-03-10 12:09:35At this point, we should be arresting, not firing, any FBI employee who delays, destroys, or withholds information on the Epstein case. There is ZERO explanation I will accept for redacting anything for “national security” reasons. A lot of Trump supporters are losing patience with Pam Bondi. I will give her the benefit of the doubt for now since the corruption within the whole security/intelligence apparatus of our country runs deep. However, let’s not forget that probably Trump’s biggest mistakes in his first term involved picking weak and easily corruptible (or blackmailable) officials. It seemed every month a formerly-loyal person did a complete 180 degree turn and did everything they could to screw him over, regardless of the betrayal’s effect on the country or whatever principles that person claimed to have. I think he’s fixed his screening process, but since we’re talking about the FBI, we know they have the power to dig up any dirt or blackmail material available, or just make it up. In the Epstein case, it’s probably better to go after Bondi than give up a treasure trove of blackmail material against the long list of members on his client list.
-
 @ 21e127ec:b43a5414
2025-03-24 22:30:47
@ 21e127ec:b43a5414
2025-03-24 22:30:47**
Respondiendo a Joel Serrano
nostr:npub1sg0j78carjndmg7qjfstk2y0e23r5cvxwn3u9z5cgnk5jnh4vxqs355u3l
respecto a hilo de Twitter sobre la adopción de Bitcoin como Medio de Intercambio con Unidad de Cuenta Delegada.
Primero, quiero compartir un artículo de Fernando Nieto que aborda la volatilidad inherente de Bitcoin:
https://x.com/fnietom/status/1454114755807961094
Este artículo de Nieto me ha llevado a cuestionarme si, en un escenario de adopción masiva, Bitcoin podría alcanzar realmente una estabilidad relativa suficiente para facilitar la coordinación de precios y el cálculo económico. De ahí surge la idea de que Bitcoin podría necesitar otros instrumentos que perfeccionen su función como unidad de cuenta.
Un ejemplo claro es lo que ocurrió en Venezuela con la dolarización de facto (al margen del Estado). En sus inicios (y aún hoy en gran medida), solo un pequeño porcentaje de la población tenía acceso a dólares a través la banca internacional, lo que les permitía realizar transacciones financieras fuera del sistema estatal. Estas operaciones se llevaban a cabo en el circuito financiero internacional, aunque las relaciones comerciales reales ocurrían dentro de Venezuela. Otro pequeño grupo tenía acceso a dólares en efectivo para sus transacciones económicas, pero la gran mayoría de la población solo disponía del bolívar venezolano como medio de intercambio en una economía dolarizada. En este contexto, muchos usaban el dólar para calcular los precios de bienes y servicios, mientras que el bolívar seguía siendo el medio de intercambio principal.
La diferencia notable con Bitcoin radica en las causas. En Venezuela, este fenómeno de medio de intercambio con unidad de cuenta delegada (Dolar - Bolivar) se debía a las restricciones monetarias impuestas por el gobierno respecto al dólar, la falta de servicios financieros en esa moneda y la escasa liquidez de dólares físicos. En el caso de Bitcoin, seria debido a su volatilidad inherente producto de su oferta inelástica (Bitcoin como medio de intercambio generalmente aceptado con unidad de cuenta delegada en Fiat publico ó privado - stablecoin).
Sin embargo, esto no implica que la unidad de cuenta que complemente a Bitcoin deba ser necesariamente emitida por un Estado. Creo que la verdadera innovación de Bitcoin radica en su potencial para actuar como un patrón monetario que descentralice la emisión monetaria de los estados gracias al monopolio de la violencia, algo que sí podían ejercer con el oro. Con Bitcoin, el Estado pierde el control, permitiendo que la banca libre emita monedas estables respaldadas en un patrón Bitcoin. El escenario sería una competencia entre monedas estables adoptadas en un segundo plano para facilitar el cálculo económico necesario para coordinar precios, préstamos, servicios financieros y la institución del crédito. Y Bitcoin podría funcionar en primer plano principalmente como medio de intercambio.
No pienso que Bitcoin vaya a eliminar las monedas fiat o estables, ya sean públicas o privadas. Más bien, lo veo como un mecanismo disciplinador que podría prevenir los malos comportamientos monetarios.
Gracias por tu tiempo agradecido y atento a tu posible respuesta.
-
 @ 6e0ea5d6:0327f353
2025-03-24 22:11:58
@ 6e0ea5d6:0327f353
2025-03-24 22:11:58People, mio caro, mistake silence for weakness just as they mistake the shine of silver for the value of gold. Because the modern world—hysterical and theatrical—has learned to respect noise, shouting, emotional outbursts, and the endless chatter of failures who demand respect without ever having earned it. But we, who have emerged from the forge of omertà, know that the one who reacts immediately is merely begging for relevance.
A real man—and I do not refer to those who simply wear trousers, but to those who carry their name and reputation upon their shoulders—knows that humiliation is not avenged with words of promise, but with a sentence of action. And sentences, amico mio, are not uttered in impulse. They are written in silence, with permanent ink on the paper of memory.
The one who strikes back in the moment of offense reveals that he is still under the dominion of emotion. But the one who remains silent, who stands still, who looks his aggressor in the eye and does not utter a single word—he has already begun to dig, with his own hands, the symbolic grave of the one who offended him. His coldness is not the absence of pain, but the absolute mastery of it. And that is precisely why he is feared. Not because he screams, but because he thinks. Because he smiles while thinking. Because he watches while you believe he has forgotten.
In Sicily, we say that the wolf does not howl when preparing to strike—it merely crouches. The fool believes that silence is cowardice. The wise man knows it is calculation. While the world carries on with its pathetic routines and social theater, the humiliated man prepares the final stage. And on this stage, there will be no audience, no applause. Only the dry sound of justice being served. Without mercy. Without apologies. Without a second chance.
Vengeance is not an emotion. It is an art. And the first stroke in the masterpiece is control.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ b8af284d:f82c91dd
2025-03-10 08:28:07
@ b8af284d:f82c91dd
2025-03-10 08:28:07Liebe Abonnenten,
800 Milliarden Euro will die EU ausgeben, um die Ukraine und den Kontinent in ein “stählernes Stachelschwein” zu verwandeln. Deutschland selbst will künftig Verteidigungsausgaben aus der Schuldenbremse ausnehmen, was nichts anderes als eine unbegrenzte Kreditlinie für das Militär bedeutet. Hinzu kommt ein “Sondervermögen” in Höhe von 500 Milliarden Euro für Infrastruktur. Das klingt nach einem Spartopf, den man für schwere Zeiten angelegt hat. Es soll die Tatsache verschleiern, dass es sich dabei um Schulden handelt. Der vermutlich baldige Kanzler Friedrich Merz bricht damit sein Wahlversprechen, die Schuldenbremse einzuhalten. Beschließen soll das Paket noch ein abgewählter Bundestag, da im neuen wohl die Mehrheit fehlt.
Womit also ist zu rechnen, wenn demnächst fast eine Billion frisch gedruckte Euro in Drohnen, Panzer und Raketen investiert werden?

Das beste Beispiel der jüngeren Geschichte ist China: 2009 legte die chinesische Regierung das bisher größte Infrastrukturprojekt der Welt in Höhe von 440 Milliarden Euro auf. Finanziert wurde es durch günstige Kredite, die vor allem an Staatsunternehmen vergeben wurden. Nachdem die Welt nach der in den USA ausgelösten Immobilienkrise 2008 in die Rezession gerutscht war, „rettete“ dieses Paket die globale Konjunktur. China hatte zu diesem Zeitpunkt großen Bedarf an Flughäfen, Straßen und vor allem Zügen. Das Paket war riskant: Schier unbegrenztes Geld, das begrenzten Waren hinterherjagt, führt zu Inflation. Billige Kredite führen meist dazu, dass Unternehmen nicht mehr effizient wirtschaften, und Schuldenberge vor sich her wälzen.
Allerdings wurde das Geld in Produktivität investiert. Denn wenn Menschen und Waren einfacher reisen können, nimmt die Geschäftstätigkeit zu: Arbeitnehmer werden mobiler, Unternehmen konkurrenzfähiger, die Preise sinken. Die Investitionen lohnen sich also, weil sie zu mehr Wirtschaftswachstum führen. Vereinfacht gesagt: Die Schulden können zurückgezahlt werden, und am Ende bleibt noch mehr übrig. In diesem Fall führen Schulden nicht zu Inflation: Durch die gesteigerte Produktivität stehen jetzt sogar mehr Waren der Geldmenge gegenüber.
15 Jahre später kämpft die zweitgrößte Volkswirtschaft zwar noch immer mit den Problemen, die aus diesem Paket resultieren - die Immobilienkrise ist eine indirekte Folge davon. Trotzdem war das Programm ein Erfolg: die Städte, Flughäfen und vor allem Zugstrecken führten zu einer höheren wirtschaftlichen Aktivität oder Produktivität. China ist heute ein wesentlich moderneres Land als vor dem Paket, und verfügt über modernste und größte Netz aus Hochgeschwindigkeitszügen der Welt. Neue Schulden können positiv sein - wenn das Geld produktiv investiert wird.
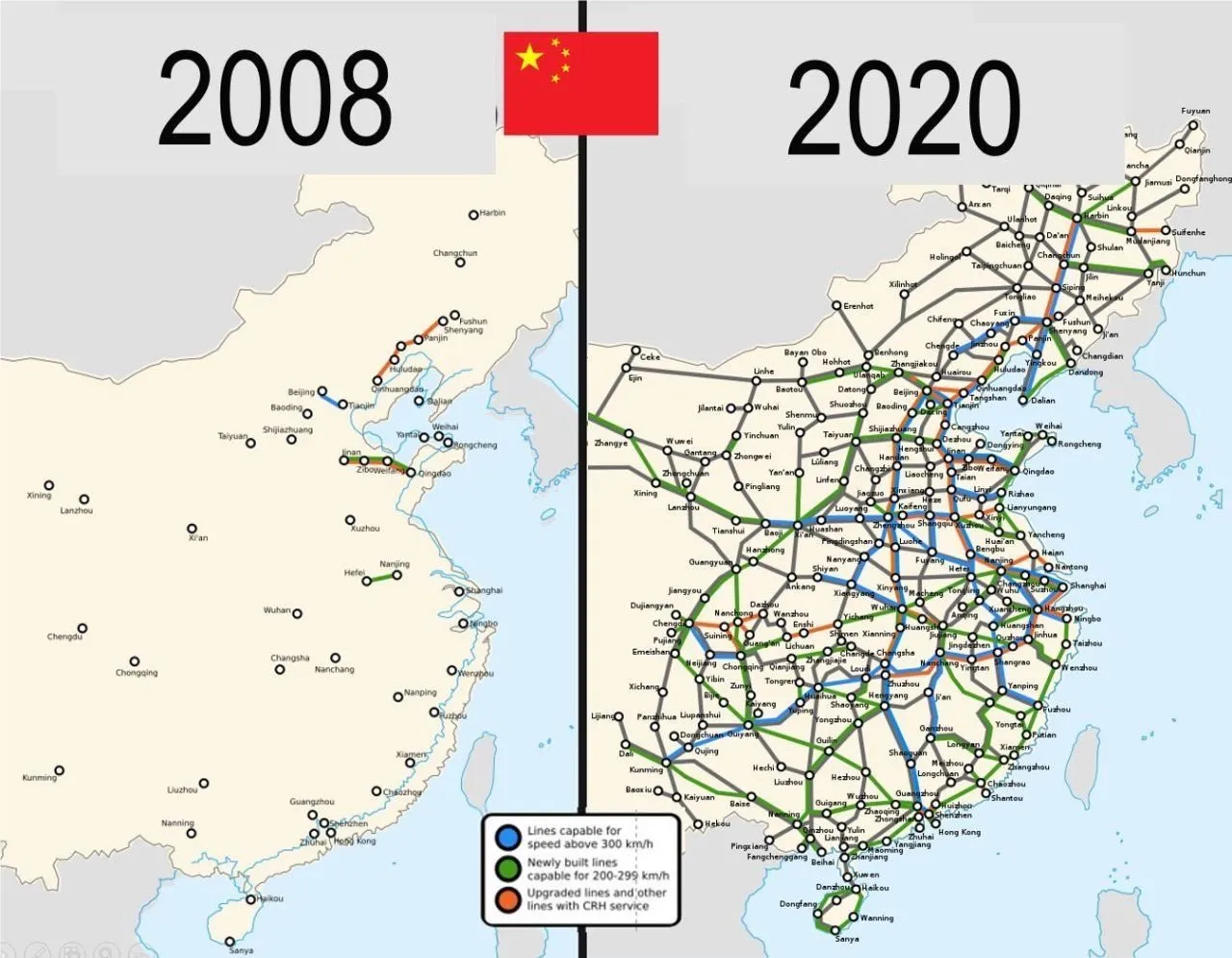
Auch in Europa lassen sich mit dem Geld-Paket zunächst mehrere Probleme auf einmal lösen: Deutschland ist noch immer ein Industriestandort mit hohen Produktionskapazitäten. Werke der Auto- und Zulieferindustrie können theoretisch zur Waffenproduktion umfunktioniert werden. Immer noch besser als sie stillzulegen oder an die Chinesen zu verkaufen, werden viele Kommentatoren schreiben.
Allein in der deutschen Automobil-Zulieferindustrie sind im vergangenen Jahr über 19000 Arbeitsplätze verloren gegangen. Viele von den Entlassenen können nun Arbeit in der Rüstungsindustrie finden. Oder wie Hans Christoph Atzpodien, Hauptgeschäftsführer des Bundesverbandes der Deutschen Sicherheits- und Verteidigungsindustrie in der WirtschaftsWoche sagt:
„Das Motto muss lauten: Autos zu Rüstung! Anstatt einen volkswirtschaftlichen Schaden durch den Niedergang der Auto-Konjunktur zu beklagen, sollten wir versuchen, Produktionseinrichtungen und vor allem Fachkräfte aus dem Automobilsektor möglichst verträglich in den Defence-Bereich zu überführen“
Immerhin: ein großer Teil des Geldes soll auch in Infrastrukturprojekte fließen: Brücken, Bahn, Internetausbau. Deutschland, und damit Europa, wird in den kommenden Monaten also eine große Party feiern, die über die Tatsache hinwegtäuschen wird, dass man einen dummen Krieg verloren hat. In den kommenden Monaten werden sich Verbände und Organisationen um das Geld reißen. Das Geld wird ein auch kollektiv-psychologisches Ventil sein, um das eigene Versagen bei Corona, Klima und Ukraine vergessen zu machen.
Es gibt allerdings einen wesentlichen Unterschied zum chinesischen Stimulus-Paket 2009: Rüstungsgüter sind im Gegensatz zu Zugstrecken totes Kapital. Eine neue Drohne oder Panzer führt nicht zu mehr Produktivität, im Gegenteil: Kommen sie zum Einsatz, zerstören sie Brücken, Häuser, Straßen und töten Menschen. Die Produktivität sinkt also. Im besten Fall kann Militärgerät herumstehen und vor sich hin rosten. Auch dann aber ist es „totes Kapital“, das nichts zur Produktivität beiträgt. Kommt es zum Einsatz, stehen der nun verringerten Warenmenge eine noch größere Geldmenge gegenüber. Die Inflation steigt.
Schleichende Militarisierung
Auch gesellschaftlich wird das Paket mit seinem Blanko-Scheck für die Verteidigungsindustrie viel verändern: Es kommt zu einer „Eichung“ der Gesellschaft, eine kollektive Abscheu des gemeinsamen Feindes. Scharfmacher, eigentlich mittelmäßiger Akademiker und Bürokraten, wie Carlo Masala und Claudia Major werden eine noch größere Rolle im öffentlichen Diskurs spielen und die Talkshows dominieren, die von einer immer älter werdenden deutschen Bevölkerung geglotzt werden. Abweichende Meinungen auf Online-Plattformen zensiert, unter dem Vorwand, die Demokratie sei in Gefahr:
Da die Rüstungsindustrie dann eine wichtigere Rolle für die Gesamtwirtschaft spielt, wird ihr Einfluss auf die Politik in Form von Lobbyisten und Verbänden zunehmen. Politiker merken schnell, dass sie von der medialen Aufmerksamkeitsökonomie nach oben gespült werden, wenn sie immer radikalere Forderungen stellen. So empfahl der ehemalige Außenminister Joschka Fischer die Woche die Wiedereinführung der Wehrpflicht für Männer und Frauen. “Star-Ökonomin” Isabella Weber will die Kriegswirtschaft mitplanen:
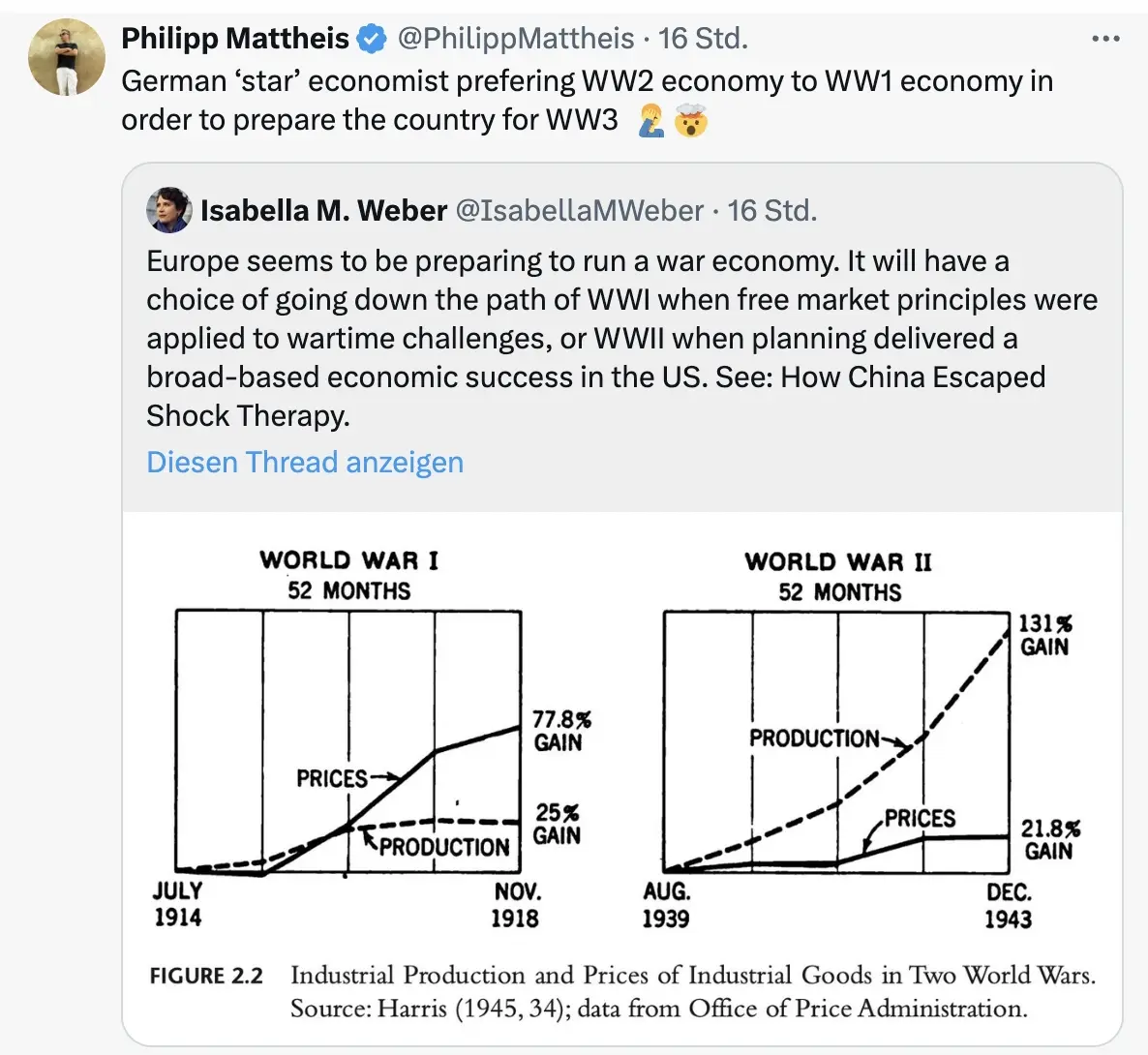
\ Der Kontinent wird sich langsam wandeln von einem „Friedensprojekt“ zu einem „metallenen Stachelschwein“, ergo Kriegsprojekt, denn ohne dämonisierten Feind funktioniert das Programm nicht. Der Ton wird rauer, autoritärer, und die Meinungsfreiheit weiter eingeschränkt werden. Die seit 2020 eingeführten Werkzeuge zur soften Propaganda („kognitive Kriegsführung”) werden verfeinert und ausgebaut werden, sodass weiterhin 80 Prozent der Bevölkerung alle noch so antihumanen Maßnahmen gutheißen werden.
Und dann?
Wie Julian Assange einmal sagte: “Das Ziel ist kein erfolgreicher Krieg. Das Ziel ist ein endloser Krieg.” Der Konflikt muss weitergehen, ewig schwelen oder ein neuer gefunden werden, da sonst ein Teil der Wirtschaftsleistung kollabiert.
Nach ein, zwei oder auch erst drei Jahren, werden erste Probleme sichtbar. Die Party endet, der Kater setzt langsam ein. Die Finanzierung an den Kapitalmärkten wird für Deutschland immer kostspieliger. Der Schuldendienst wird einen größeren Teil des Haushalts einnehmen. Die Bürger müssen dies mitfinanzieren. Der voraussichtlich neue Bundeskanzler Friedrich Merz sprach bereits von der „Mobilisierung der deutschen Sparguthaben“.
\ Was im Ersten Weltkrieg „Kriegsanleihen“ hieß, wird einen schickeren Namen bekommen wie „olivgrüne Bonds“. You name it. Alternativ lässt sich ein Verteidigungs-Soli einführen, oder das Kindergeld streichen, wie kürzlich Ifo-Chef Clemens Fuest forderte.
Was kann man tun? Auf BlingBling geht es um konkrete Tipps, welche Anlagen von dieser Entwicklung profitieren werden. Außerdem geht es um die “Strategische Bitcoin Reserve”, die am Donnerstag beschlossen wurde.
-
 @ 7d33ba57:1b82db35
2025-03-24 21:47:31
@ 7d33ba57:1b82db35
2025-03-24 21:47:31Located on the southeastern coast of Spain, Cartagena is a city rich in history, maritime heritage, and stunning Mediterranean views. With over 3,000 years of history, it boasts Roman ruins, modernist architecture, and a vibrant port, making it one of Spain’s most underrated travel destinations.
🏛️ Top Things to See & Do in Cartagena
1️⃣ Roman Theatre of Cartagena 🎭
- The star attraction, dating back to the 1st century BC.
- One of Spain’s best-preserved Roman theatres, discovered in 1988 beneath the city.
- Visit the museum to learn about its history before exploring the impressive ruins.
2️⃣ Concepción Castle & Panoramic Lift 🏰
- A 14th-century fortress on a hill offering spectacular views of the city and harbor.
- Take the glass elevator for a scenic ride to the top.
- The museum inside explains Cartagena’s rich military and naval history.
3️⃣ Calle Mayor & Modernist Architecture 🏛️
- The city’s main pedestrian street, lined with elegant buildings, shops, and cafés.
- Admire Casa Cervantes, Gran Hotel, and the Casino, examples of Cartagena’s modernist style.
4️⃣ National Museum of Underwater Archaeology (ARQVA) ⚓
- Learn about sunken treasures, ancient shipwrecks, and underwater archaeology.
- Features artifacts from Phoenician, Roman, and medieval maritime history.
5️⃣ Naval Museum & the Peral Submarine 🚢
- Discover Cartagena’s naval history, including models of warships and maritime artifacts.
- See the Peral Submarine, the first-ever electric-powered submarine, invented in 1888.
6️⃣ Playa de Cala Cortina 🏖️
- A beautiful urban beach, just a few minutes from the city center.
- Great for swimming, snorkeling, and relaxing with clear Mediterranean waters.
7️⃣ Batería de Castillitos 🏰
- A dramatic cliffside fortress with fairy-tale turrets and massive coastal cannons.
- Located 30 minutes from Cartagena, offering panoramic sea views.
🍽️ What to Eat in Cartagena
- Caldero del Mar Menor – A local seafood rice dish, similar to paella 🍚🐟
- Michirones – A hearty bean stew with chorizo and ham 🥘
- Marineras – A Russian salad tapa served on a breadstick with an anchovy 🥖🐟
- Tarta de la abuela – A delicious layered biscuit and chocolate cake 🍰
- Asiático Coffee – A signature Cartagena coffee with condensed milk, brandy, and cinnamon ☕🍸
🚗 How to Get to Cartagena
🚆 By Train: Direct trains from Madrid (4 hrs), Murcia (45 min), and Alicante (1.5 hrs)
🚘 By Car: ~30 min from Murcia, 1.5 hrs from Alicante, 3.5 hrs from Madrid
✈️ By Air: Nearest airport is Murcia-Corvera Airport (RMU) (~30 min away)
🚢 By Cruise Ship: Cartagena is a popular Mediterranean cruise stop💡 Tips for Visiting Cartagena
✅ Best time to visit? Spring & Autumn – warm but not too hot 🌞
✅ Wear comfortable shoes – Many streets and attractions involve walking on cobblestones 👟
✅ Visit during the Roman Festival (Carthaginians & Romans, September) for a unique cultural experience 🎭🏛️
✅ Try a sunset drink at a rooftop bar near the port for incredible views 🍹🌅 -
 @ f3873798:24b3f2f3
2025-03-10 00:32:44
@ f3873798:24b3f2f3
2025-03-10 00:32:44Recentemente, assisti a um vídeo que me fez refletir profundamente sobre o impacto da linguagem na hora de vender. No vídeo, uma jovem relatava sua experiência ao presenciar um vendedor de amendoim em uma agência dos Correios. O local estava cheio, as pessoas aguardavam impacientes na fila e, em meio a esse cenário, um homem humilde tentava vender seu produto. Mas sua abordagem não era estratégica; ao invés de destacar os benefícios do amendoim, ele suplicava para que alguém o ajudasse comprando. O resultado? Ninguém se interessou.

A jovem observou que o problema não era o produto, mas a forma como ele estava sendo oferecido. Afinal, muitas das pessoas ali estavam há horas esperando e perto do horário do almoço – o amendoim poderia ser um ótimo tira-gosto. No entanto, como a comunicação do vendedor vinha carregada de desespero, ele afastava os clientes ao invés de atraí-los. Esse vídeo me tocou profundamente.
No dia seguinte, ao sair para comemorar meu aniversário, vi um menino vendendo balas na rua, sob o sol forte. Assim como no caso do amendoim, percebi que as pessoas ao redor não se interessavam por seu produto. Ao se aproximar do carro, resolvi comprar dois pacotes. Mais do que ajudar, queria que aquele pequeno gesto servisse como incentivo para que ele continuasse acreditando no seu negócio.
Essa experiência me fez refletir ainda mais sobre o poder da comunicação em vendas. Muitas vezes, não é o produto que está errado, mas sim a forma como o vendedor o apresenta. Quando transmitimos confiança e mostramos o valor do que vendemos, despertamos o interesse genuíno dos clientes.
Como a Linguagem Impacta as Vendas?

1. O Poder da Abordagem Positiva
Em vez de pedir por ajuda, é importante destacar os benefícios do produto. No caso do amendoim, o vendedor poderia ter dito algo como: "Que tal um petisco delicioso enquanto espera? Um amendoim fresquinho para matar a fome até o almoço!"
2. A Emoção na Medida Certa
Expressar emoção é essencial, mas sem parecer desesperado. Os clientes devem sentir que estão adquirindo algo de valor, não apenas ajudando o vendedor.
3. Conheça Seu Público
Entender o contexto é fundamental. Se as pessoas estavam com fome e impacientes, uma abordagem mais objetiva e focada no benefício do produto poderia gerar mais vendas.
4. Autoconfiança e Postura
Falar com firmeza e segurança transmite credibilidade. O vendedor precisa acreditar no próprio produto antes de convencer o cliente a comprá-lo.
Conclusão
Vender é mais do que apenas oferecer um produto – é uma arte que envolve comunicação, percepção e estratégia. Pequenos ajustes na abordagem podem transformar completamente os resultados. Se o vendedor de amendoim tivesse apresentado seu produto de outra maneira, talvez tivesse vendido tudo rapidamente. Da mesma forma, se cada um de nós aprender a se comunicar melhor em nossas próprias áreas, poderemos alcançar muito mais sucesso.
E você? Já passou por uma experiência parecida?
-
 @ 4925ea33:025410d8
2025-03-08 00:38:48
@ 4925ea33:025410d8
2025-03-08 00:38:481. O que é um Aromaterapeuta?

O aromaterapeuta é um profissional especializado na prática da Aromaterapia, responsável pelo uso adequado de óleos essenciais, ervas aromáticas, águas florais e destilados herbais para fins terapêuticos.
A atuação desse profissional envolve diferentes métodos de aplicação, como inalação, uso tópico, sempre considerando a segurança e a necessidade individual do cliente. A Aromaterapia pode auxiliar na redução do estresse, alívio de dores crônicas, relaxamento muscular e melhora da respiração, entre outros benefícios.
Além disso, os aromaterapeutas podem trabalhar em conjunto com outros profissionais da saúde para oferecer um tratamento complementar em diversas condições. Como já mencionado no artigo sobre "Como evitar processos alérgicos na prática da Aromaterapia", é essencial ter acompanhamento profissional, pois os óleos essenciais são altamente concentrados e podem causar reações adversas se utilizados de forma inadequada.
2. Como um Aromaterapeuta Pode Ajudar?

Você pode procurar um aromaterapeuta para diferentes necessidades, como:
✔ Questões Emocionais e Psicológicas
Auxílio em momentos de luto, divórcio, demissão ou outras situações desafiadoras.
Apoio na redução do estresse, ansiedade e insônia.
Vale lembrar que, em casos de transtornos psiquiátricos, a Aromaterapia deve ser usada como terapia complementar, associada ao tratamento médico.
✔ Questões Físicas
Dores musculares e articulares.
Problemas respiratórios como rinite, sinusite e tosse.
Distúrbios digestivos leves.
Dores de cabeça e enxaquecas. Nesses casos, a Aromaterapia pode ser um suporte, mas não substitui a medicina tradicional para identificar a origem dos sintomas.
✔ Saúde da Pele e Cabelos
Tratamento para acne, dermatites e psoríase.
Cuidados com o envelhecimento precoce da pele.
Redução da queda de cabelo e controle da oleosidade do couro cabeludo.
✔ Bem-estar e Qualidade de Vida
Melhora da concentração e foco, aumentando a produtividade.
Estímulo da disposição e energia.
Auxílio no equilíbrio hormonal (TPM, menopausa, desequilíbrios hormonais).
Com base nessas necessidades, o aromaterapeuta irá indicar o melhor tratamento, calculando doses, sinergias (combinação de óleos essenciais), diluições e técnicas de aplicação, como inalação, uso tópico ou difusão.
3. Como Funciona uma Consulta com um Aromaterapeuta?

Uma consulta com um aromaterapeuta é um atendimento personalizado, onde são avaliadas as necessidades do cliente para a criação de um protocolo adequado. O processo geralmente segue estas etapas:
✔ Anamnese (Entrevista Inicial)
Perguntas sobre saúde física, emocional e estilo de vida.
Levantamento de sintomas, histórico médico e possíveis alergias.
Definição dos objetivos da terapia (alívio do estresse, melhora do sono, dores musculares etc.).
✔ Escolha dos Óleos Essenciais
Seleção dos óleos mais indicados para o caso.
Consideração das propriedades terapêuticas, contraindicações e combinações seguras.
✔ Definição do Método de Uso
O profissional indicará a melhor forma de aplicação, que pode ser:
Inalação: difusores, colares aromáticos, vaporização.
Uso tópico: massagens, óleos corporais, compressas.
Banhos aromáticos e escalda-pés. Todas as diluições serão ajustadas de acordo com a segurança e a necessidade individual do cliente.
✔ Plano de Acompanhamento
Instruções detalhadas sobre o uso correto dos óleos essenciais.
Orientação sobre frequência e duração do tratamento.
Possibilidade de retorno para ajustes no protocolo.
A consulta pode ser realizada presencialmente ou online, dependendo do profissional.
Quer saber como a Aromaterapia pode te ajudar? Agende uma consulta comigo e descubra os benefícios dos óleos essenciais para o seu bem-estar!
-
 @ ec9bd746:df11a9d0
2025-03-07 20:13:38
@ ec9bd746:df11a9d0
2025-03-07 20:13:38I was diving into PoW (Proof-of-Work) once again after nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq3wamnwvaz7tmjv4kxz7fwdehhxarj9e3xzmny9uqzqj8a67jths8euy33v5yu6me6ngua5v3y3qq3dswuqh2pejmtls6datagmu rekindled my interest with his PoW Draw project. It was a fun little trifle, but it shifted my focus just the right way at the right time.
Because then, on Friday, came the Oval Office Travesty. Once I got over the initial shock, I decided I couldn't just curse and lament; I needed to do something bigger, something symbolic, something expressive. So that's exactly what I did—breaking nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq32amnwvaz7tmjv4kxz7fwv3sk6atn9e5k7tcqyqewrqnkx4zsaweutf739s0cu7et29zrntqs5elw70vlm8zudr3y2t9v7jg's record which he held for almost 2 and half years.
Here is a note with PoW 45, the highest PoW known to Nostr (as of now).
nostr:nevent1qvzqqqqqqypzpmym6ar92346qc04ml08z6j0yrelylkv9r9ysurhte0g2003r2wsqy88wumn8ghj7mn0wvhxcmmv9uqsuamnwvaz7tmwdaejumr0dshsqgqqqqqqqqqy8t8awr5c8z4yfp4cr8v7spp8psncv8twlh083flcr582fyu9
How Did I Pull It Off?
In theory, quite simple: Create note, run PoW mining script & wait.
Thanks to PoW Draw, I already had mining software at hand: nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq32amnwvaz7tmjv4kxz7fwv3sk6atn9e5k7tcqyqvqc5tlvn6etv09f0fvuauves49dvgnukjtzsndfv9y8yyrqyxmz7dty6z's notemine_hw, but when you know that there is a 1 in 2^45 chance that the next hash will be the correct one you want to increase the odds a bit. So on Monday evening, I started my Note Mining operation on an old 40 thread machine called Workhorse.
Issues Along the Way
I was immediately surprised that Workhorse (2× Intel Xeon Silver 4114) produced only about 3Mh/s. A laptop (Intel Core i7-1185G7) with Windows and all the bloat did 5Mh/s. That was strange.
Another hurdle was that notemine_hw does not refresh the
created_atfield. With just a few Mh/s of power I was potentially looking at weeks of computation, by then the note would be quite stale. So I created systemd service leveraging theRuntimeMaxSecoption to periodically restart every 3600 seconds assuring that the Note would be max 1 hour old at the time of publishing.Luckily PoW is that kind of problem where every hash attempt is an independent event, so the chance of success is the same whether you do it in small increments or one uninterrupted stretch. So by restarting the mining process I was only losing a few mere seconds every hour due to the overhead.
Once the note staleness issue was resolved, I looked at the 40 workers on Workhorse vs. 7 workers on the laptop and start messing around with running one instance with 40 workers and running 40 instances with 1 worker and found out, that the workers are not bound to a CPU thread and are jumping between the CPUs like rabbits high on Colombian carrots.
The solution? Running multiple instances with one worker each as a service locked to its own CPU core using systemd's
CPUAffinityoption. ``` $aida@workhorse:systemd/system $ sudo cat notemine@.service [Unit] Description=Notemine HW Publish (restarts hourly)[Service] Type=simple CPUAffinity=%i
The command to run:
ExecStart=/home/aida/.cargo/bin/notemine_hw publish --n-workers 1 --difficulty 45 --event-json /home/aida/note.json --relay-url 'wss://wot.shaving.kiwi' --nsec nsec0123456789abcdef
Let the process run for 1 hour (3600 seconds), then systemd will stop it:
RuntimeMaxSec=3600 TimeoutStopSec=1
Tells systemd to restart the service automatically after it stops:
Restart=always RestartSec=1
run as a non-root user:
User=aida Group=aida
[Install] WantedBy=multi-user.target ``` Then I added a starting service to spawn an instance for each CPU thread.
``` $aida@workhorse:systemd/system $ sudo cat notemine_start.service [Unit] Description=Start all services in sequence with 3-second intervals
[Service] Type=oneshot ExecStart=/usr/bin/zsh /home/aida/notemine_start.sh
RemainAfterExit=yes
[Install] WantedBy=multi-user.target
Here is the startup script (I know, loops exist—but Ctrl+C/Ctrl+V is so old-school):aida@workhorse:~ $ cat notemine_start.sh /usr/bin/systemctl start notemine@0.service /usr/bin/sleep 3 /usr/bin/systemctl start notemine@1.service /usr/bin/sleep 3 /usr/bin/systemctl start notemine@2.service /usr/bin/sleep 3 /usr/bin/systemctl start notemine@3.service /usr/bin/sleep 3 ... ... ... /usr/bin/systemctl start notemine@38.service`` The sleep there is critical to make sure that thecreated_at`timestamps are different, preventing redundant hashing.This adjustment made Workhorse the strongest machine in my fleet with 10+Mh/s.
The Luck Aspect
From Monday evening, I started adding all machines at my disposal into the fleet and by Wednesday evening I was crunching hashes on about 130 CPU threads (a lot of them were quite antique) and at the peak was just little shy of 40Mh/s. To compensate for the slow start with the few above-mentioned hiccups and the fact that I had to use my desktop to do other things from time to time, I counted with the conservative estimate of 30Mh/s when I was doing all the probability calculations.
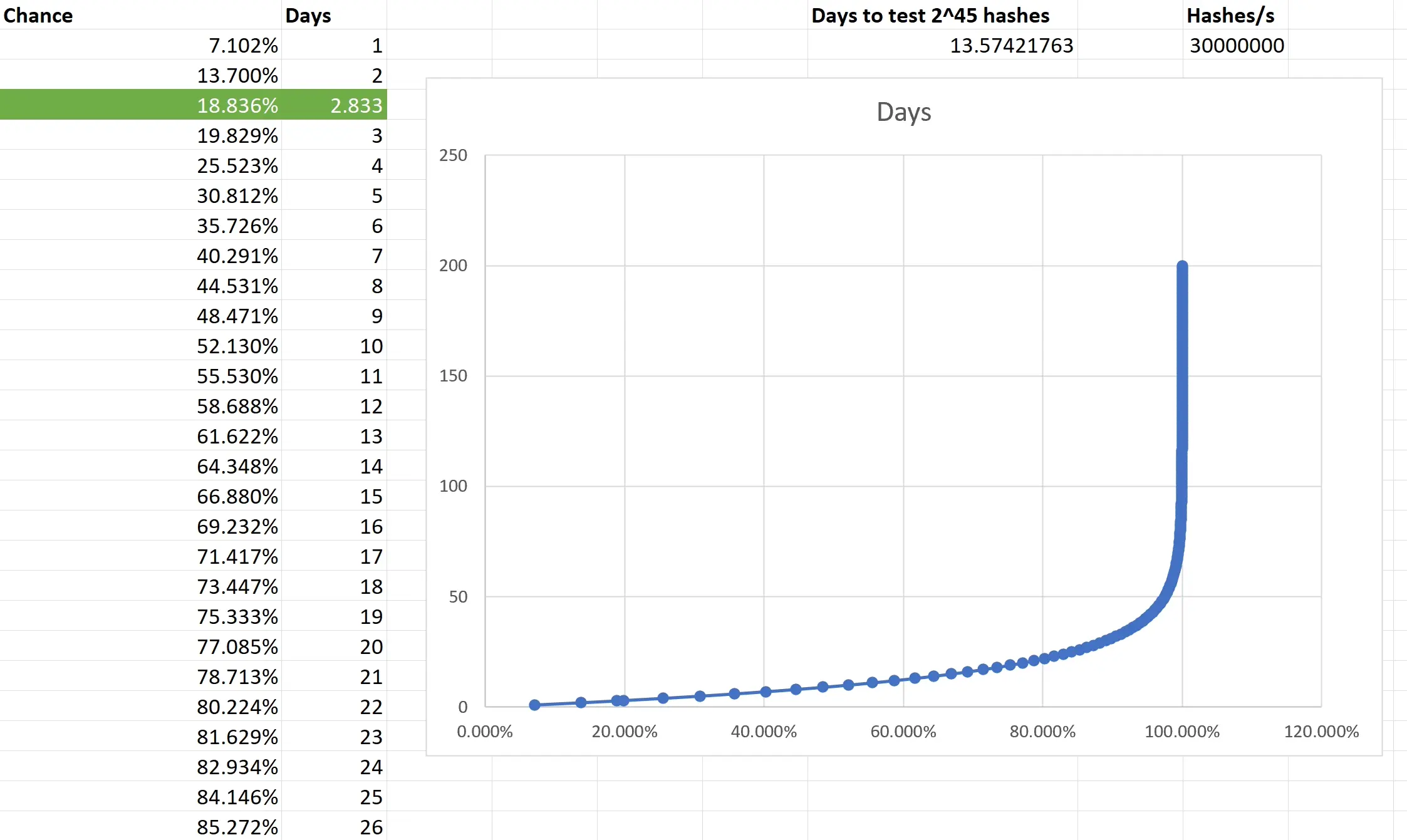
Based on the type of task that PoW mining is, the outcome is not predictible. You are only looking at what is the chance that the outcome of every single independent event will be consecutively non-favourable and then subtracting it from 1 to get the chance of that single favourable event you want. I really had to brush up on my combinatorics and discrete mathematics to make sure I have at least an elementary understanding of what is going on. Also, because we are not just throwing a dice 5 times, but are operating with big numbers, approximation was necessary. Luckily, the formula is available and quite simple in the end.
Two weeks to exhauste all the possible tries still doesn't guarantee anything, actually there is a slighlty less than 2 in 3 chance that you will have a result after all that time. So the fact that I was able to hit the right hash in less than 3 days was good luck. Not insane lottery winning luck, but good luck; slighlty lower than 1 in 5.
Do you want to beat me?
Go ahead! All the pitfalls are described above and until there is a GPU-based PoW Mining available, we are all on pretty even ground.
Do you hate the note?
In that case, feel free to enjoy this accompanying image:

-
 @ 04c915da:3dfbecc9
2025-03-07 00:26:37
@ 04c915da:3dfbecc9
2025-03-07 00:26:37There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ 878dff7c:037d18bc
2025-03-24 21:43:00
@ 878dff7c:037d18bc
2025-03-24 21:43:00China Denies Plans to Send Peacekeeping Troops to Ukraine
Summary:
Recent reports suggested that China was considering participating in a European-led peacekeeping mission in Ukraine. However, the Chinese Foreign Ministry has firmly denied these claims, stating that such reports are "completely untrue" and reaffirming China's consistent and clear position on the Ukraine crisis. This development highlights the complexities in international efforts to address the ongoing conflict in Ukraine.
Sources: Politico - March 25, 2025, Global Times - March 25, 2025, Newsweek - March 25, 2025
Internal Environmental Regulations Pose Greater Threat to Australian Trade Than Foreign Tariffs
Summary:
Australia's stringent environmental regulations, referred to as "green tape," are posing significant risks to its export industries, including LNG, coal, and iron ore. These regulations have drawn criticism from key trading partners like Japan. The Albanese government's commitments under international climate agreements have intensified these regulations, potentially undermining economic stability more than foreign tariffs.
Sources: The Daily Telegraph - March 25, 2025
Government Announces 'Buy Australian' Initiative to Support Local Industries
Summary:
In response to global trade uncertainties, the Albanese government has introduced a 'Buy Australian' policy aimed at bolstering domestic industries and reducing reliance on international markets. The initiative seeks to mitigate the impact of foreign tariffs and promote local manufacturing, aligning with efforts to 'Trump-proof' the Australian economy against external economic policies.
Source: News.com.au - March 25, 2025
Interest Rates Expected to Remain Elevated Amid Global Trade Tensions
Summary:
Economic analysts predict that the Reserve Bank of Australia may maintain higher interest rates for an extended period due to anticipated inflationary pressures stemming from global trade tensions. Policies, such as tariffs imposed by the U.S., are contributing to economic uncertainty, potentially impacting Australia's economic stability and influencing monetary policy decisions.
Source: News.com.au - March 25, 2025
Severe Flooding Threatens Queensland Amid Heavy Rainfall
Summary:
Queensland is experiencing severe weather conditions, with heavy rainfall leading to significant flooding risks. The Bureau of Meteorology has issued warnings for severe thunderstorms and flooding, particularly between Innisfail and Townsville. In the past 24 hours, rainfall totals have ranged from 50 to 150mm, with expectations of up to 200mm in isolated areas. Major flood warnings are in effect for the Bulloo River, with moderate warnings for several others. Inland regions could see up to 400mm, equating to nearly a year's worth of rain. Residents are advised to stay updated and prepare for potential emergencies.
Sources: News.com.au - 25 March 2025, The Guardian - 25 March 2025
Peter Dutton's 'Me Too' Politics Strategy Criticized Within Liberal Party
Summary:
Peter Dutton's approach of rapidly matching Labor's spending pledges, such as the $8.5 billion Medicare boost and a $150 power bill rebate, has drawn criticism within the Liberal Party. This "Me Too" strategy aims to appear equally voter-friendly but is argued to undermine the Coalition's credibility as better economic managers amid a cost-of-living crisis. Critics suggest that by mirroring Labor's spending, the Coalition loses the ability to effectively critique Labor's fiscal policies without appearing hypocritical, potentially benefiting Labor as their spending gains voter favor.
Sources: The Daily Telegraph - March 24, 2025
Community Organizations Oppose Proposed Public Housing Reforms in Northern Territory
Summary:
Community organizations are criticizing the Country Liberal Party's proposed public housing reforms, which aim to address anti-social behavior, evictions, and debt. Critics argue these reforms could negatively impact disadvantaged groups, particularly Aboriginal Territorians, by shifting the perception of housing from a human right to a conditional privilege. The Central Land Council warns of potential increases in homelessness and incarceration rates among Aboriginal people.
Sources: The Courier-Mail - 25 March 2025
Coalition Proposes Changes to Vehicle Emissions Standards and Hybrid Tax Incentives
Summary:
The Coalition plans to modify Labor’s vehicle emissions standards and reinstate tax incentives for plug-in hybrids. They argue that removing these incentives could hinder efforts to reduce emissions and negatively impact Australian families during the current cost-of-living crisis. The car industry also expresses concerns about stringent carbon footprint targets and the financial burden of meeting emission requirements.
Sources: The Australian - 25 March 2025
Call for Development of Sovereign Supply Chains in Australia
Summary:
A recent survey revealed that 63% of company leaders view geopolitical instability as the primary risk to their organizations. The pandemic exposed vulnerabilities in global and domestic supply chains, particularly in Australia's production of essential goods. To address this, there is a call for developing resilient sovereign supply chains, balancing reshoring critical manufacturing with strategic partnerships. Collaborative efforts across government, business, and educational institutions are deemed necessary to build robust supply chains.
Sources: The Australian - 25 March 2025
Interest Rates in Australia May Stay High Amid Global Economic Uncertainty
Summary:
Interest rates in Australia may remain elevated due to expected increases in inflation, driven by U.S. tariff policies causing global economic uncertainty. These tariffs are likely to raise prices and contribute to inflationary pressures. The Reserve Bank of Australia faces a dilemma, balancing the need to address declining employment data with the potential for rate cuts to stimulate the economy. Economists suggest maintaining current interest rates to observe further economic developments.
Sources: News.com.au - 25 March 2025
NSW Government to Remove Shark Nets from Sydney Beaches
Summary:
The NSW government will remove shark nets from 51 Sydney beaches on March 31, ahead of their usual end-of-April schedule, to reduce the bycatch of sea turtles migrating throughout April. This decision follows feedback from coastal councils, six of which have voted for the permanent removal of the nets due to concerns over marine bycatch. However, there are concerns that alternative shark mitigation technologies, such as drones and SMART drumlines, may not be as effective in protecting swimmers. The final decision on the future of the shark nets will be made by the NSW government, based on a report compiled from the feedback of 25 councils.
Sources: The Daily Telegraph - March 24, 2025
Victoria Achieves World-Leading Cardiac Arrest Survival Rates
Summary:
Victoria has quietly become a global leader in cardiac arrest survival, thanks to a combination of fast emergency responses, community training, and public health infrastructure. New data released today shows that 41% of people who suffered a cardiac arrest in public and received immediate CPR and defibrillation survived — putting Victoria among the top three regions globally, just behind King County in the U.S. and Denmark.
Much of the credit goes to everyday citizens. Nearly 80% of cardiac arrests witnessed by bystanders were met with immediate CPR, a rate far above the national average. The widespread rollout of over 7,500 publicly accessible defibrillators and the GoodSAM mobile app — which alerts nearby trained responders in real-time — has also played a key role in improving outcomes.
Health officials say the results are proof that early intervention saves lives, and the state's model could serve as a blueprint for others. Survivors and their families have expressed overwhelming gratitude for both the emergency responders and ordinary citizens whose quick thinking made the difference.
Sources: The Guardian - March 24, 2025, ABC News - March 25, 2025
Wind Drought Challenges Australia's Renewable Energy Sector
Summary:
Zen Energy, co-developed by economist Ross Garnaut, is facing financial difficulties due to a "wind drought" affecting its wind generation capacity. The company had to purchase expensive spot market capacity to meet obligations, leading to the sale of a near 10% stake for $43 million to fund large-scale battery development. This situation highlights the challenges in Australia's transition to renewable energy, especially with fluctuating wholesale electricity prices and long-term contracts.
Sources: The Australian - March 24, 2025
Istanbul Mayor's Arrest Signals Turkey's Authoritarian Shift
Summary:
Ekrem Imamoglu, the mayor of Istanbul and a prominent opposition figure, has been detained and jailed on charges of graft and terrorism. Analysts suggest that President Recep Tayyip Erdogan's move was facilitated by global geopolitical instability, reducing the likelihood of international condemnation. This arrest is viewed as a significant blow to Turkish opposition and indicative of a move towards increased authoritarianism.
Sources: Associated Press - March 25, 2025
Iranian Generals Direct Houthi Attacks in Red Sea
Summary:
Key Iranian figures behind Houthi rebel operations in Yemen have been identified. The Houthis, supported by Iran's IRGC, have launched attacks on merchant vessels and warships in the Red Sea, disrupting global trade. These operations are reportedly commanded by senior Iranian officials and approved by Supreme Leader Ali Khamenei, highlighting Iran's strategic involvement in regional conflicts.
Sources: The Sun - March 22, 2025
Exploring Programming, AI, and Personal Journeys with ThePrimeagen on the Lex Fridman Podcast
Summary:
In episode #461 of the Lex Fridman Podcast, Lex has an in-depth conversation with ThePrimeagen, a well-known software developer and content creator. The episode covers a range of topics including:
- Programming and Development: ThePrimeagen shares insights into modern coding practices, the evolution of software engineering, and his passion for low-level programming.
- Artificial Intelligence: The two discuss AI's impact on society, the future of intelligent systems, and philosophical implications.
- Life with ADHD: ThePrimeagen opens up about living with ADHD, discussing the challenges it brings and how he channels it into productivity.
- Addiction and Recovery: A personal and vulnerable look at his journey through addiction and the steps he took toward recovery.
- Philosophy and Faith: The episode also touches on topics like belief in God, human purpose, and finding meaning through both faith and technology.
Importance:
This episode stands out for its honest blend of technical depth and emotional vulnerability. It offers listeners a rare look at how a high-performing developer balances the pressures of tech life with personal challenges. The philosophical undertones add a reflective layer, making it not just informative but also deeply human.
Sources: Lex Fridman Podcast - March 25, 2025
-
 @ 4520e45a:aa52208a
2025-03-24 21:42:12
@ 4520e45a:aa52208a
2025-03-24 21:42:12Hashrate\ Die Hashrate wird vom Pool basierend auf den übermittelten Shares innerhalb eines Zeitraums berechnet und zeigt, wie viele Hashes pro Sekunde dein Worker generiert.\ Die Statistik zeigt die durschschnittliche Hashrate für:\ 1 Minute (1m), 5 Minuten (5m), 1 Stunde (1hr), 1 Tag (1d), 7 Tage (7d)
1M = 1 MH/s = 1'000'000 H/S\ 1G = 1 GH/s = 1'000'000'000 H/S\ 1T = 1 TH/s = 1'000'000'000'000 H/S\ 1P = 1 PH/s = 1'000'000'000'000'000 H/S
Lastshare\ Angabe in Unix Zeit, wann der letzte Share von deinem Worker bei ckpool abgeliefert wurde.\ 🔗 unix timestamp converter
Worker\ Anzahl Worker. Wenn mehrere Miner identischen Namen haben, werden sie zu einem Worker zusammengefasst. Wenn du für jeden Miner separate Statistiken willst, muss sich deren Worker-Name hinter der Bitcoin-Adresse unterscheiden:\ 1CCAV1N3FCffp4fXBBAF6qNGu1tvXTmndy.bitaxe1\ 1CCAV1N3FCffp4fXBBAF6qNGu1tvXTmndy.bitaxe2\ 1CCAV1N3FCffp4fXBBAF6qNGu1tvXTmndy.bitaxe3
Shares\ Anzahl akzeptierter Shares, die seit Beginn von deinem Worker bei ckpool abgeliefert wurden. Wenn ein Hash alle notwendigen Kriterien und die vom Pool geforderte Schwierigkeit erfüllt, wird er als Share an ckpool übermittelt.
Bestshare\ Der beste/höchste Share der seit dem letzten gefundenen Block abgeliefert wurde.\ Wenn du oder ckpool einen Block gefunden hat, wird dieser Wert zurück auf Null gesetzt.
Bestever\ Der jemals beste/höchste gefundene Share. Im AxeOS als Best Difficulty bezeichnet.\ Wenn du oder ckpool einen Block gefunden hat, wird dieser Wert nicht zurück auf Null gesetzt.
Ein Block wird gefunden, wenn die Schwierigkeit (=Difficulty) eines Shares höher ist als die aktuelle Netzwerk-Schwierigkeit.
Zum Zeitpunkt des Schreibens des Reads — Blockzeit 889277 — liegt die Netzwerk-Schwierigkeit bei: 113'757'508'810'854 = 113T
Authorised\ Angabe in Unix Zeit, wann du dich zum ersten Mal mit ckpool verbunden hast (wurde erst mit v0.9.7 am 30.05.2023 eingeführt).\ 🔗 unix timestamp converter
-
 @ 6389be64:ef439d32
2025-02-27 21:32:12
@ 6389be64:ef439d32
2025-02-27 21:32:12GA, plebs. The latest episode of Bitcoin And is out, and, as always, the chicanery is running rampant. Let’s break down the biggest topics I covered, and if you want the full, unfiltered rant, make sure to listen to the episode linked below.
House Democrats’ MEME Act: A Bad Joke?
House Democrats are proposing a bill to ban presidential meme coins, clearly aimed at Trump’s and Melania’s ill-advised token launches. While grifters launching meme coins is bad, this bill is just as ridiculous. If this legislation moves forward, expect a retaliatory strike exposing how politicians like Pelosi and Warren mysteriously amassed their fortunes. Will it pass? Doubtful. But it’s another sign of the government’s obsession with regulating everything except itself.
Senate Banking’s First Digital Asset Hearing: The Real Target Is You
Cynthia Lummis chaired the first digital asset hearing, and—surprise!—it was all about control. The discussion centered on stablecoins, AML, and KYC regulations, with witnesses suggesting Orwellian measures like freezing stablecoin transactions unless pre-approved by authorities. What was barely mentioned? Bitcoin. They want full oversight of stablecoins, which is really about controlling financial freedom. Expect more nonsense targeting self-custody wallets under the guise of stopping “bad actors.”
Bank of America and PayPal Want In on Stablecoins
Bank of America’s CEO openly stated they’ll launch a stablecoin as soon as regulation allows. Meanwhile, PayPal’s CEO paid for a hat using Bitcoin—not their own stablecoin, Pi USD. Why wouldn’t he use his own product? Maybe he knows stablecoins aren’t what they’re hyped up to be. Either way, the legacy financial system is gearing up to flood the market with stablecoins, not because they love crypto, but because it’s a tool to extend U.S. dollar dominance.
MetaPlanet Buys the Dip
Japan’s MetaPlanet issued $13.4M in bonds to buy more Bitcoin, proving once again that institutions see the writing on the wall. Unlike U.S. regulators who obsess over stablecoins, some companies are actually stacking sats.
UK Expands Crypto Seizure Powers
Across the pond, the UK government is pushing legislation to make it easier to seize and destroy crypto linked to criminal activity. While they frame it as going after the bad guys, it’s another move toward centralized control and financial surveillance.
Bitcoin Tools & Tech: Arc, SatoChip, and Nunchuk
Some bullish Bitcoin developments: ARC v0.5 is making Bitcoin’s second layer more efficient, SatoChip now supports Taproot and Nostr, and Nunchuk launched a group wallet with chat, making multisig collaboration easier.
The Bottom Line
The state is coming for financial privacy and control, and stablecoins are their weapon of choice. Bitcoiners need to stay focused, keep their coins in self-custody, and build out parallel systems. Expect more regulatory attacks, but don’t let them distract you—just keep stacking and transacting in ways they can’t control.
🎧 Listen to the full episode here: https://fountain.fm/episode/PYITCo18AJnsEkKLz2Ks
💰 Support the show by boosting sats on Podcasting 2.0! and I will see you on the other side.
-
 @ b2d670de:907f9d4a
2025-02-26 18:27:47
@ b2d670de:907f9d4a
2025-02-26 18:27:47This is a list of nostr clients exposed as onion services. The list is currently actively maintained on GitHub. Contributions are always appreciated!
| Client name | Onion URL | Source code URL | Admin | Description | | --- | --- | --- | --- | --- | | Snort | http://agzj5a4be3kgp6yurijk4q7pm2yh4a5nphdg4zozk365yirf7ahuctyd.onion | https://git.v0l.io/Kieran/snort | operator | N/A | | moStard | http://sifbugd5nwdq77plmidkug4y57zuqwqio3zlyreizrhejhp6bohfwkad.onion/ | https://github.com/rafael-xmr/nostrudel/tree/mostard | operator | minimalist monero friendly nostrudel fork | | Nostrudel | http://oxtrnmb4wsb77rmk64q3jfr55fo33luwmsyaoovicyhzgrulleiojsad.onion/ | https://github.com/hzrd149/nostrudel | operator | Runs latest tagged docker image | | Nostrudel Next | http://oxtrnnumsflm7hmvb3xqphed2eqpbrt4seflgmdsjnpgc3ejd6iycuyd.onion/ | https://github.com/hzrd149/nostrudel | operator | Runs latest "next" tagged docker image | | Nsite | http://q457mvdt5smqj726m4lsqxxdyx7r3v7gufzt46zbkop6mkghpnr7z3qd.onion/ | https://github.com/hzrd149/nsite-ts | operator | Runs nsite. You can read more about nsite here. | | Shopstr | http://6fkdn756yryd5wurkq7ifnexupnfwj6sotbtby2xhj5baythl4cyf2id.onion/ | https://github.com/shopstr-eng/shopstr-hidden-service | operator | Runs the latest
serverlessbranch build of Shopstr. | -
 @ ed5774ac:45611c5c
2025-03-24 21:33:47
@ ed5774ac:45611c5c
2025-03-24 21:33:47Erdogan’s Turkey: The Rise, Reign, and Decline of a Political Strongman
As Turkey’s political crisis intensifies with Erdogan’s imprisonment of Imamoglu—a leading opposition figure and likely frontrunner in the 2028 presidential elections—it is crucial to analyze the historical events and geopolitical factors that enabled Erdogan’s rise, secured the consolidation of his rule, and allowed him to maintain his grip on power for decades. To understand the foundations of Erdogan’s enduring political legacy, we must examine the historical events that shaped his ideology and the global power struggles of the time. Equally important are the international actors who facilitated his rise and prolonged his rule. Key factors include the link between Erdogan’s rise and the Iraq War, the interplay between Turkey’s military coups and the Ukraine crisis, the events that led to the erosion of Western support for Erdogan, the role of the U.S. and NATO in the 2016 coup attempt against his rule, and the shifting geopolitical landscape that continues to define Turkey’s political future.
The Roots of Islamism: The CIA, the 1980 Coup, and the Suppression of Turkish Liberalism
Erdogan’s rise is deeply intertwined with the growth of Turkey’s Islamic movement, which gained traction in the 1970s amid Cold War geopolitics. During this period, the U.S., under the guidance of Zbigniew Brzezinski, National Security Advisor to President Jimmy Carter, devised the “Green Belt” strategy. This plan aimed to cultivate a radicalized Islamic generation across the Muslim world to counter the spread of communist ideology. The U.S. intervention in Afghanistan, which radicalized certain factions and triggered the Soviet invasion, was a critical component of this strategy. Brzezinski himself proudly acknowledged this in various interviews. Turkey, a NATO ally bordering the Soviet Union, became a key theater for implementing this policy.
The military coup of September 12, 1980, marked a pivotal moment in Turkish history. Led by General Kenan Evren, the Turkish armed forces seized power under the pretext of restoring order amid escalating violence between leftist and rightist factions that had claimed thousands of lives. However, the junta’s crackdown disproportionately targeted the Turkish left—a movement distinct from Soviet-style communism, composed of liberal, educated intellectuals such as writers, artists, journalists, and thinkers. These individuals, who championed Turkish sovereignty, intellectual freedom, and democratic ideals, were perceived as a direct threat to the military’s Islamization agenda, backed by the CIA. Tens of thousands were imprisoned, tortured, or executed, while left-wing organizations were banned outright.
At the same time, the junta actively fostered Islamist groups, establishing religious schools known as Imam Hatip institutions under the guise of combating Marxism and communism. In reality, their true objective was to eliminate anyone who sought Turkish sovereignty, embraced patriotism, or valued critical thinking. Writers, artists, journalists, and intellectuals—those who dared to think independently and question authority—were viewed as existential threats to the Islamization model the military and its CIA allies sought to impose. By silencing these voices, the junta aimed to eradicate opposition to their vision of a Turkey subservient to religious dogma and foreign interests, ensuring a populace stripped of sovereign thought and resistant to enlightenment.
This paradox—a secular military suppressing liberal intellectuals while nurturing Islamist groups—laid the foundation for Erdogan’s rise and the eventual Islamization of Turkish society.
The Chaos of the 1990s: Economic Crisis and the Rise of Erdogan
The 1990s were a chaotic decade for Turkey, marked by economic instability, a Kurdish insurgency, and a revolving door of coalition governments. The 1994 financial crisis saw inflation soar, while terrorist attacks by the Kurdistan Workers’ Party (PKK) and political assassinations fueled national disarray. Successive governments, often beholden to globalist agendas dictated by the International Monetary Fund and World Bank, failed to deliver stability. This period mirrored today’s European political crises, where ideological convergence has left voters disillusioned.
Into this void stepped Erdogan, a charismatic former soccer player turned politician from Istanbul’s working-class Kasimpasa district, whose blend of populist appeal and religious rhetoric resonated with a disillusioned populace. His rise was no accident. In 1994, he won the mayoralty of Istanbul as a member of the Islamist Welfare Party (Refah Partisi), showcasing a blend of populist charisma and religious appeal. However, his early political career faced a setback in 1997 when the military, acting as guardians of Turkey’s secular Kemalist legacy, forced the resignation of Welfare Party Prime Minister Necmettin Erbakan in what was dubbed a “postmodern coup.” Erdogan’s imprisonment in 1998 for reciting a divisive poem only solidified his image as a martyr among his devout supporters.
The 2001 Crisis: Neocons, Economic Sabotage, and Erdogan’s Ascendancy
Erdogan’s true ascent began amid Turkey’s devastating 2001 financial crisis, which saw the economy contract by 5.7%, unemployment spike, and the Turkish lira collapse. The crisis, worsened by IMF-mandated austerity measures, discredited the ruling coalition under Prime Minister Bulent Ecevit. A staunch nationalist, Ecevit had spearheaded Turkey’s 1974 intervention in Cyprus and forced Syria to expel PKK leader Abdullah Ocalan in 1999. His refusal to align Turkey with the impending U.S.-led Iraq War in 2003 made him a liability for U.S. neoconservatives, who were already preparing for the conflict.
Far from a mere economic downturn, the 2001 crisis was a deliberate strategy orchestrated by the global Western financial cartel to destabilize Ecevit’s nationalist government. This administration, fiercely protective of Turkish sovereignty, had unequivocally opposed Turkey’s involvement in the Iraq War. To eliminate this obstacle, the financial cartel—comprising international financial institutions and Western-backed actors—engineered the crisis by exploiting Turkey’s reliance on hot money and Western financial support. The resulting economic collapse eroded public trust in the government and existing political parties, creating a power vacuum that paved the way for Erdogan. Handpicked by the globalist cabal as their new proxy, Erdogan was positioned to advance their political agenda in Turkey. The neocons viewed him as a pliable ally: a moderate Islamist who could pacify Turkey’s religious conservatives while advancing Western interests. Despite resistance within his own party, Erdogan advocated for Turkish involvement in the Iraq War, though the Turkish Parliament, with the help of dissidents in his party, ultimately rejected U.S. troop deployments in 2003. Nevertheless, Erdogan remained loyal to his neocon backers and globalist patrons, privatizing state assets at rock-bottom prices—akin to Yeltsin’s controversial reforms in 1990s Russia—and deepening Turkey’s economic dependence on the EU and the U.S.
In addition to tying Turkey’s economy to Western interests, Erdogan targeted the Turkish military in 2007 through the Ergenekon and Sledgehammer trials. Widely criticized as show trials orchestrated with the help of the Gulen movement—a shadowy Islamic network led by Fethullah Gulen—these cases imprisoned or sidelined hundreds of officers, including navy admirals opposed to NATO’s Black Sea ambitions. These officers had long argued that NATO’s mission ended with the fall of the Soviet Union and advocated for closer ties with Russia and China. They also opposed plans to integrate Georgia and Ukraine into NATO, fearing it would destabilize the region and turn the Black Sea into a battleground between the West and Russia. By weakening the navy and sidelining its dissenting admirals, Erdogan brought Turkey back in line with NATO’s strategic objectives, enabling the neocons to advance their plans for NATO expansion into the Black Sea region—a move that set the stage for the 2008 Russo-Georgian War and the 2014 Ukrainian crisis.. Without this internal coup against the Turkish military, these events might have unfolded differently—or not at all.
For his services to the globalist agenda, Erdogan was portrayed in Western media as a democratizing hero, and Turkey’s economy was praised for its growth and strength. However, the reality was starkly different. To understand the globalist propaganda surrounding Erdogan, consider Barack Obama’s first foreign visit as U.S. president: a trip to Turkey in 2009. In a speech to the Turkish Parliament, Obama praised Erdogan’s “democratic reforms” and the strength of Turkey’s economy—which was growing steadily only due to cheap credit provided by international financial institutions serving the same globalist interests Erdogan represented. Meanwhile, journalists and dissidents filled Turkish prisons.
The 2016 Coup Attempt: Erdogan’s Break with the West
Erdogan’s honeymoon with the West soured in the 2010s. His support for Egypt’s Muslim Brotherhood and his interventionist stance in Syria clashed with U.S. priorities, especially after the Arab Spring upended regional alliances. Sensing Erdogan’s growing autonomy, the neocons turned to Fethullah Gulen, a cleric living in Pennsylvania since 1999 with close ties to the CIA and the Clinton Foundation. Gulen’s Hizmet movement, once an ally in Erdogan’s rise, had infiltrated Turkey’s police, judiciary, and military, creating a “parallel state.”
The July 15, 2016, coup attempt—marked by rogue military units bombing parliament and nearly capturing Erdogan—was orchestrated by factions of the Gulen movement within the army, with the involvement of the CIA and NATO, using Incirlik Air Base as one of the primary command centers to coordinate the operation (one of NATO’s largest military bases in the region). The timing suggests that the neocons, anticipating Hillary Clinton’s presidency, planned to install Gulen as their new puppet in Turkey. As a radical Sunni leader hostile to Iran, Gulen could have aligned Turkey with a broader anti-Iranian axis, potentially dragging the country into a regional war against Iran—much like Saddam Hussein did three decades earlier.
The coup’s failure, quashed by loyalists and public resistance, marked a turning point, leading Erdogan to purge over 100,000 civil servants and consolidate his power through a 2017 referendum and pivoting toward Russia and China—not out of conviction, but as leverage against Western abandonment.
Turkey’s Geopolitical Balancing Act: Ukraine, NATO, and the Black Sea
Erdogan’s post-2016 flirtations with Moscow—evidenced by the purchase of Russian S-400 systems and energy deals—reflect more than a pragmatic balancing act. They reflect a desperate attempt to regain Western attention, akin to dating someone new to make an ex jealous, aimed at convincing the West not to write him off.
The Ukrainian crisis, escalating with Russia’s 2022 invasion, has pushed Turkey into a delicate role. As a NATO member controlling the Bosphorus, Erdogan has mediated grain deals and prisoner swaps, leveraging Turkey’s strategic position. Yet his reluctance to fully back NATO’s hardline stance has further alienated him from the West, making him a target for a potential regime change operation as the West has grown desperate to win its proxy war against Russia. As a result, international media and globalist factions have intensified efforts to undermine his regime, seeking to remove him from power.
Turkey at a Crossroads: Imamoglu, Erdogan’s Decline, and the Future
Erdogan has fulfilled his mission: he has made Turkey’s economy dependent on the West, eliminated patriotic voices in the military, dismantled the parliamentary system, wrecked the education system, and buried the secular Turkish republic. His legacy is a deeply polarized Turkey: economically dependent on the West, militarily weakened, and institutionally hollowed out.
Corruption scandals, a collapsing lira, and authoritarian excesses have fueled widespread public discontent. Yet, rather than addressing the root causes of this anger—economic hardship, growing authoritarianism, and systemic corruption—Erdogan has grown increasingly paranoid, attributing every challenge to Western conspiracies and interventions. This refusal to confront reality has only deepened the divide between him and the Turkish people, fueling widespread disillusionment and anger.
Imamoglu’s rise—winning Istanbul in 2019 and 2023 despite blatant election irregularities, systematic government interference, censorship, and the full force of Erdogan’s authoritarian machinery—stands as a testament to his resilience and the enduring hope of Turkey’s opposition. Facing a system rigged to ensure his defeat, Imamoglu triumphed against overwhelming odds. Erdogan’s regime spared no effort, leveraging state media, the judiciary, and security forces to manipulate the results, yet it could not prevent Imamoglu’s victories in Istanbul, which shattered the illusion of invincibility surrounding Erdogan’s rule. His recent imprisonment on fabricated charges ahead of the 2028 elections underscores Erdogan’s desperation to suppress this threat, further alienating a populace yearning for change.
Turkey now stands at a crossroads. The powers that once propelled Erdogan to prominence—U.S. neoconservatives and the Islamist legacy of the 1980 coup—have lost control of their creation. His fall from Western favor, tied to the 2016 coup attempt and his regional overreach, has left him isolated, oscillating between East and West while clinging to power as domestic anger reaches a boiling point. Whether Imamoglu or another leader emerges, Turkey’s post-Erdogan era will face the monumental task of rebuilding its secular republic and defining its role in an increasingly complex global landscape.
Turkey’s struggle is not just its own—it is an example of the suffering endured for decades under Western colonialism and a parasitic financial order. This system, designed to enrich a handful of elites in the West, thrives by exploiting the Global South, perpetuating poverty, and engineering chaos to maintain control. Turkey’s fight for self-determination stands as a beacon for all nations seeking to break free from the chains of neocolonialism and reclaim their rightful place in a just and equitable global order. The future must be built on the sovereignty of nations, free from the selfish designs of a Western oligarchy.
-
 @ b8851a06:9b120ba1
2025-02-22 19:43:13
@ b8851a06:9b120ba1
2025-02-22 19:43:13The digital guillotine has fallen. The Bybit hack wasn’t just a theft—it was a surgical strike exposing the fatal flaw of “crypto” that isn’t Bitcoin. This wasn’t a bug. It was a feature of a system designed to fail.
Here’s how North Korea’s Lazarus Group stole $1.5B in ETH, why “decentralized finance” is a joke, and how Bitcoin remains the only exit from this circus.
I. The Heist: How Centralized “Crypto” Betrayed Its Users
A. The Multisig Mousetrap (Or: Why You’re Still Using a Bank)
Bybit’s Ethereum cold wallet used multisig, requiring multiple approvals for transactions. Sounds secure, right? Wrong. • The Con: Hackers didn’t pick the lock; they tricked the keyholders using a UI masking attack. The wallet interface showed “SEND TO BYBIT”, but the smart contract was whispering “SEND TO PYONGYANG.” • Bitcoin Parallel: Bitcoin’s multisig is enforced on hardware, not a website UI. No browser spoofing, no phishing emails—just raw cryptography.
Ethereum’s multisig is a vault with a touchscreen PIN pad. Bitcoin’s is a mechanical safe with a key only you hold. Guess which one got robbed?
B. Smart Contracts: Dumb as a Bag of Hammers
The thieves didn’t “hack” Ethereum—they exploited its smart contract complexity. • Bybit’s security depended on a Safe.global contract. Lazarus simply tricked Bybit into approving a malicious upgrade. • Imagine a vending machine that’s programmed to take your money but never give you a soda. That’s Ethereum’s “trustless” tech.
Why Bitcoin Wins: Bitcoin doesn’t do “smart contracts” in the Ethereum sense. Its scripting language is deliberately limited—less code, fewer attack vectors.
Ethereum is a Lego tower; Bitcoin is a granite slab. One topples, one doesn’t.
II. The Laundering: Crypto’s Dirty Little Secret
A. Mixers, Bridges, and the Art of Spycraft
Once the ETH was stolen, Lazarus laundered it at lightspeed: 1. Mixers (eXch) – Obfuscating transaction trails. 2. Bridges (Chainflip) – Swapping ETH for Bitcoin because that’s the only exit that matters.
Bitcoin Reality Check: Bitcoin’s privacy tools (like CoinJoin) are self-custodial—no third-party mixers. You keep control, not some “decentralized” website waiting to be hacked.
Ethereum’s “bridges” are burning rope ladders. Bitcoin’s privacy? An underground tunnel only you control.
B. The $1.5B Lie: “Decentralized” Exchanges Are a Myth
Bybit’s “cold wallet” was on Safe.global—a so-called “decentralized” custodian. Translation? A website with extra steps. • When Safe.global got breached, the private keys were stolen instantly. • “Decentralized” means nothing if your funds depend on one website, one server, one weak link.
Bitcoin’s Answer: Self-custody. Hardware wallets. Cold storage. No trusted third parties.
Using Safe.global is like hiding your life savings in a gym locker labeled “STEAL ME.”
III. The Culprits: State-Sponsored Hackers & Crypto’s Original Sin
A. Lazarus Group: Crypto’s Robin Hood (For Dictators)
North Korea’s hackers didn’t break cryptography—they broke people. • Phishing emails disguised as job offers. • Bribes & social engineering targeting insiders. • DeFi governance manipulation (because Proof-of-Stake is just shareholder voting in disguise).
Bitcoin’s Shield: No CEO to bribe. No “upgrade buttons” to exploit. No governance tokens to manipulate. Code is law—and Bitcoin’s law is written in stone.
Ethereum’s security model is “trust us.” Bitcoin’s is “verify.”
B. The $3B Elephant: Altcoins Fund Dictators
Since 2017, Lazarus has stolen $3B+ in crypto, funding North Korea’s missile program.
Why? Because Ethereum, Solana, and XRP are built on Proof-of-Stake (PoS)—which centralizes power in the hands of a few rich validators. • Bitcoin’s Proof-of-Work: Miners secure the network through energy-backed cryptography. • Altcoins’ Proof-of-Stake: Security is dictated by who owns the most tokens.
Proof-of-Stake secures oligarchs. Proof-of-Work secures money. That’s why Lazarus can drain altcoin treasuries but hasn’t touched Bitcoin’s network.
IV. Bybit’s Survival: A Centralized Circus
A. The Bailout: Banks 2.0
Bybit took bridge loans from “undisclosed partners” (read: Wall Street vultures). • Just like a traditional bank, Bybit printed liquidity out of thin air to stay solvent. • If that sounds familiar, it’s because crypto exchanges are just banks in hoodies.
Bitcoin Contrast: No loans. No bailouts. No “trust.” Just 21 million coins, mathematically secured.
Bybit’s solvency is a confidence trick. Bitcoin’s solvency is math.
B. The Great Withdrawal Panic
Within hours, 350,000+ users scrambled to withdraw funds.
A digital bank run—except this isn’t a bank. It’s an exchange that pretended to be decentralized.
Bitcoin fixes this: your wallet isn’t an IOU. It’s actual money.
Bybit = a TikTok influencer promising riches. Bitcoin = the gold in your basement.
V. The Fallout: Regulators vs Reality
A. ETH’s 8% Crash vs Bitcoin’s Unshakable Base
Ethereum tanked because it’s a tech stock, not money. Bitcoin? Dropped 2% and stabilized.
No CEO, no headquarters, no attack surface.
B. The Regulatory Trap
Now the bureaucrats come in demanding: 1. Wallet audits (they don’t understand public ledgers). 2. Mixer bans (criminalizing privacy). 3. KYC everything (turning crypto into a surveillance state).
Bitcoin’s Rebellion: You can’t audit what’s already transparent. You can’t ban what’s unstoppable.
VI. Conclusion: Burn the Altcoins, Stack the Sats
The Bybit hack isn’t a crypto problem. It’s an altcoin problem.
Ethereum’s smart contracts, DeFi bridges, and “decentralized” wallets are Swiss cheese for hackers. Bitcoin? A titanium vault.
The Only Lessons That Matter:
✅ Multisig isn’t enough unless it’s Bitcoin’s hardware-enforced version. ✅ Complexity kills—every altcoin “innovation” is a security risk waiting to happen.
Lazarus Group won this round because “crypto” ignored Bitcoin’s design. The solution isn’t better regulations—it’s better money.
Burn the tokens. Unplug the servers. Bitcoin is the exit.
Take your money off exchanges. Be sovereign.
-
 @ 0028f12f:532c1c67
2025-03-24 21:23:28
@ 0028f12f:532c1c67
2025-03-24 21:23:28An owner buildable microhome closed-loop ecosystem that decentralizes residential manufacturing w/ancient & modern tools, materials, and skillsets.


Project Overview:
For many, whether renters or “owners”, monthly housing costs are 30%, sometimes 50% of their monthly operating expenses, with financing, permitting, maintenance, and property tax costs significantly driving those costs ever higher. As a result, low-cost, efficient to build and maintain, modular shelters are more needed than ever. By combining ancient, 20th century, and 21st century technologies humanity can now self-design, fund, and build decentralized pre-manufactured, site-installed, residential living systems for ourselves.
Decentralizing residential construction in order to empower individuals and their communities by providing cottage industries that build small cottages with tools, training, and flexible, simple, and appropriate designs will not only provide sovereignty over shelter to owner-builders, it creates the potential for organically growing physical community infrastructures and individual’s financial wealth.
Accomplishing this requires:
- Off-the-shelf tools available at most major hardware stores worldwide. i.e. no expensive, capital intensive, difficult to operate and/or maintain tooling
- Commonly available, or easily acquirable, skills with those tools
- Locally available, low-cost, sustainable, materials with a minimal environmental impact
- Prioritizing “upcycled” materials diverted from the waste stream
- Non-toxic, durable, yet, easy to repair materials
- Utilizing site resourced materials whenever feasible
- Integrated design that stacks functions, turns waste streams into resources (i.e. grey gardens, Composting worms and fly larvae, natural gas bio-digesters, aquaponics garden/pools)
- Self-funding without taking on debt burdens, permission, and/or insurance agents having authority over the decision-making processes
As E. F. Schumacher showed us in his book “Small is Beautiful”, Christopher Alexander with “Pattern Language Design”, and Bill Mollison with “Permaculture Design”, an appropriately scaled design pattern that can be varied as needed for each use case and location is what we all need and desire. Empowering individual families and communities to truly OWN their homes, because the idea, skills, and experience needed to build them have become common knowledge available to any and all willing to do the work.
Residential housing has been artificially driven up in value by speculators because the “saving” function of fiat money is broken and their prices are not driven by their functional value, financing and compliance costs make owning a home even more expensive, and poor design decisions by gatekeepers provide poor value, and dependency on specialized tools and skillsets drives up maintenance costs. Waste during initial, repair, and remodeling construction match all other daily waste going to the landfills, while chemical fire retardants, plastics, and glues often create toxic interior air quality worse than outside. Dozens of specialized crews that do not communicate with or understand others’ roles, needs, and concerns leading to wasted time, money, and materials.
Might not the best solution to the current housing affordability crisis simply be to provide families, not with over-priced, over-sized, and overly regulated shelters, but to instead empower all us to design and build decentralized, anti-fragile, and sustainable residential living systems that shelter more than our bodies and possessions_. Homes that also_ preserve and protect the supply chains for our essential daily needs. All of humanity, in every culture on every continent in every climate will be empowered by acquiring useful trade skills that can provide, not only for their own daily needs, but also deliver the opportunity to earn ongoing right livelihood providing these same livingry services to our local communities.
What if…
- In a few weeks the tradecrafts could be acquired, that with commonly accessible and affordable tools, empower men and women everywhere to use renewable, sustainable, and locally available materials to build residential living ecosystems that, rather than consume, they produce capital over time in the form of:
- Soil, Plant, Animal, & Human food
- Water for gardens & all inhabitants
- Fuel for heating & cooking
- KwHrs to run appliances, fixtures, & tools
- Bitcoin to access global marketplaces
- Government “permitting”, zoning, insurance, and financing startup costs are reduced & often eliminated.
- Operational costs and maintenance labor are minimized, efficiency and production increase over time, and wastes streams are turned into resource streams.
- The physical, intellectual, financial, and experiential capital are re-invested into serving family and neighbors by creating a decentralized open-source cooperative cottage construction industry
Building Biology, or "Bau-Biologie" in German, provides us with a mental for our Pattern Language design stack that allows for biomimicry and biophilic design to evolve into a synergistic “macrobiome” that shows us the way to design and build living residential “super organisms”. Our house is not only our ‘3rd Skin’, the property line is the 4th skin, acting as the outermost semi-permeable protective layer of our residential ecosystems.
The How:
By designing visible and invisible structures so that human, animal, plant, & soil organisms are ALL working together to coordinate a single living, breathing, growing entity. One with biological electrical ‘nervous system’ that cultivates, stores, & distributes electrical power, that has a ‘digestive system’ that provides for fresh water collection, filtration, & distribution, as well as grey/black water disposal. With a respiratory, skeletal, and connective tissues, organs, and systems, that nourish and protect essential organs.
By designing in more than just shelter, it becomes possible to provide all inhabitants with fuel for cooking and heating generated from passive solar heating, methane biodigesters, wood-gas/wind/water/PV generators, and BTC mining. Buckminster Fuller’s work showed us that geodesic domes are the most efficient geometries to use, and experience over time with residential domes has taught many that including a cupola and a dormer-style clerestory facilitate naturally efficient lighting and ventilation. While 3d printing, thin-shell latex cement canvas, and styro-foam concrete technologies now empower us all to design,manufacture, and build the joints, skin, and insulative in-fill for these geometric shapes in any configuration we can imagine. Adding space age insulative ceramic micro-spheres creates a non-toxic flexible highly reflective exterior coating suitable for rainwater collection and stacking the Japanese Shou Sugi Ban ancient natural wood preservation protects and beautifies the often up-cycled wood skeletal elements.
By riding on the efficiencies of scale that already exist for trampoline frames, both new and re-purposed, the existing manufacturing, distribution, and packaging of these galvanized steel skeletal framing elements we can add the wood, plastic, fabric, and cement elements as needed for each use case for this basic structural design unit. The lightweight framing, skinning, and insulation these allow for also enable more areas to become inhabitable by mounting these to docks enable residential use currently unavailable flood plane land and for Lake-steading, and eventually Sea-steading. By keeping the roofing footprint under 200 sq ft, the permitting threshold in many cities like Austin, TX the compliance costs of permitting and zoning are eliminated. By keeping costs down to 5-figures, instead of the 6 & 7-figures spent building most modern day homes, doing so with finance and insurance costs that can be kept to a minimum and sometimes eliminated.
Concept MVP
 Individually shouldering the responsibility for designing, building, and maintaining the infrastructure for sheltering our families and our business assets is now more possible by stacking our designs, tools, and materials on the shoulders of designers, engineers, and owner-builders from all other times, places, and cultures.
Individually shouldering the responsibility for designing, building, and maintaining the infrastructure for sheltering our families and our business assets is now more possible by stacking our designs, tools, and materials on the shoulders of designers, engineers, and owner-builders from all other times, places, and cultures.I built this roof of this 200 sq ft micro-dome igloo in a semi-permanent minimum viable form entirely by myself over a few months with under $3k spent on tools and materials.
 The final piece of this jigsaw puzzle came when I gained access to 3d printing technology I began printing brackets for a 2v dome. The free model that I found was sized so that a single cut on an 8’ board would provide the two lengths of struts needed without any waste. (https://www.thingiverse.com/thing:2483498). The initial model design happened to form a 14’ diameter hemisphere, with a 7’ height. I then realized that the upcycled trampoline frames made a superior vertical “pony wall” as is commonly used to gain more headroom around the interior perimeter of dome structures. By using 2”x12” wood with double beveled cuts to form a 14’ octagon I created a ledge that the dome could be mounted to, that also provides a mounting surface for guttering to enable rainwater catchment
The final piece of this jigsaw puzzle came when I gained access to 3d printing technology I began printing brackets for a 2v dome. The free model that I found was sized so that a single cut on an 8’ board would provide the two lengths of struts needed without any waste. (https://www.thingiverse.com/thing:2483498). The initial model design happened to form a 14’ diameter hemisphere, with a 7’ height. I then realized that the upcycled trampoline frames made a superior vertical “pony wall” as is commonly used to gain more headroom around the interior perimeter of dome structures. By using 2”x12” wood with double beveled cuts to form a 14’ octagon I created a ledge that the dome could be mounted to, that also provides a mounting surface for guttering to enable rainwater catchment The vertical poles and angled connecters from the trampoline happened to be 7’ in width, allowing for a 7’x7’ square addition to the 14’ diameter circle. The 140 sq ft of the trampoline and the 49 sq ft add-on, at 189 in total came in just under the 199 sq ft maximum allowed without a permit. This shape took form as a geodesic igloo. When I contemplated upon the partial skeletal framework for awhile before “skinning” the structure I decided that turning the 5 triangles coming off the corners of the pentagon cupola would not only provide dispersed light from any/all directions it also allowed for leaving those opening until last to allow for applying the finishing coats to the uppermost pentagon of the dome. After considering ways to keep from putting a window in the roof, with the likelihood for leaks that brings, I came up with the idea of the 5 triangular dormer style windows that are easier to seal and prevent direct sunlight while allowing indirect daylight from all sides into the dome interior. Those triangular dormers, along with the cupola vents and wall perimeter vents can be opened and closed to create and control passive ventilation
The vertical poles and angled connecters from the trampoline happened to be 7’ in width, allowing for a 7’x7’ square addition to the 14’ diameter circle. The 140 sq ft of the trampoline and the 49 sq ft add-on, at 189 in total came in just under the 199 sq ft maximum allowed without a permit. This shape took form as a geodesic igloo. When I contemplated upon the partial skeletal framework for awhile before “skinning” the structure I decided that turning the 5 triangles coming off the corners of the pentagon cupola would not only provide dispersed light from any/all directions it also allowed for leaving those opening until last to allow for applying the finishing coats to the uppermost pentagon of the dome. After considering ways to keep from putting a window in the roof, with the likelihood for leaks that brings, I came up with the idea of the 5 triangular dormer style windows that are easier to seal and prevent direct sunlight while allowing indirect daylight from all sides into the dome interior. Those triangular dormers, along with the cupola vents and wall perimeter vents can be opened and closed to create and control passive ventilation For the next, permanent version designed for occupancy by a couple I’m raising this current 30” wall to a full 8’ height to allow for a living/sleeping loft under the dome hemisphere. In order to support a second floor, arranging the floor joists in a hub and spoke layout bolted directly to the 1 ½” galvanized steel vertical support poles of the trampoline “oreo” framework. By supporting the central hub with the stair framing, rather than dropping a pole from the center of the peak of the dome, a ceiling fan can be mounted there instead to circulate air when the wind isn’t blowing. By using only 2 x 8’x4’ sheets of plywood for the floor of the private living/sleeping loft only 64 sq ft of floor space is necessary, as a wall mounted desk and mounting shelves for a futon frame as the kitchen ceiling will keep the bed from taking up precious floor space, while maximizing functionality of every cubic foot of the micro-dome igloo. The framing for the stairs provided an interior shower/toilet closet, preferably a sawdust “humanure” composting toilet to collect “night soil” in order to return nutrients back to the garden soil. Having an optional add-on door that opens into an IBC tote double-stack “outhouse” with a bio-gas generating flush toilet and another door opening up to an outdoor shower draining into greywater gardens and mulch basins, not only automates watering the garden while providing nutrients, it also allows for the natural gas to be used to fuel a cookstove, hot water heater, or natural gas generator.
For the next, permanent version designed for occupancy by a couple I’m raising this current 30” wall to a full 8’ height to allow for a living/sleeping loft under the dome hemisphere. In order to support a second floor, arranging the floor joists in a hub and spoke layout bolted directly to the 1 ½” galvanized steel vertical support poles of the trampoline “oreo” framework. By supporting the central hub with the stair framing, rather than dropping a pole from the center of the peak of the dome, a ceiling fan can be mounted there instead to circulate air when the wind isn’t blowing. By using only 2 x 8’x4’ sheets of plywood for the floor of the private living/sleeping loft only 64 sq ft of floor space is necessary, as a wall mounted desk and mounting shelves for a futon frame as the kitchen ceiling will keep the bed from taking up precious floor space, while maximizing functionality of every cubic foot of the micro-dome igloo. The framing for the stairs provided an interior shower/toilet closet, preferably a sawdust “humanure” composting toilet to collect “night soil” in order to return nutrients back to the garden soil. Having an optional add-on door that opens into an IBC tote double-stack “outhouse” with a bio-gas generating flush toilet and another door opening up to an outdoor shower draining into greywater gardens and mulch basins, not only automates watering the garden while providing nutrients, it also allows for the natural gas to be used to fuel a cookstove, hot water heater, or natural gas generator. Strategically, this is an advanced version of the Gradual Stiffening pattern, as articulated in the Pattern Language Design dictionary created by Christopher Alexander. Other patterns like Bringing the Outside In, which the passive lighting and ventilation features contribute to, and Intimacy Gradient, which the upstairs private/downstairs public uses of space create, came from his design library. Other design pattern strategies coming from Bill Mollison’s ideas shared in his Permaculture Design Manual, like Stack Functions, Transform Waste into Resource, and a Resource Harvesting Roof.
Strategically, this is an advanced version of the Gradual Stiffening pattern, as articulated in the Pattern Language Design dictionary created by Christopher Alexander. Other patterns like Bringing the Outside In, which the passive lighting and ventilation features contribute to, and Intimacy Gradient, which the upstairs private/downstairs public uses of space create, came from his design library. Other design pattern strategies coming from Bill Mollison’s ideas shared in his Permaculture Design Manual, like Stack Functions, Transform Waste into Resource, and a Resource Harvesting Roof. Collecting water, heat, and photons by tactically implementing grey-water gardens, the methane bio-digesters, the humanure composting/BSFL cultivation, passive solar water heater and PV systems, as well as wood-gas generator upgrades. By re-purposing the existing trampoline manufacturing infrastructure, adding 3d design and printing, and upcycled “re-blended” paint from the city recycling center, the capital to manufacture the steel and mats are minimized, landfill waste is diverted into a resource while cutting costs.
 At the same time, by training local craftsmen with on-the-job vocational technology education the tools and skills necessary for establishing e
ssential infrastructure for cottage industry that build cottages for local community members. By doing so we can minimize upfront capital costs, lower environmental impact, and contribute to empowering community members with right livelihood, as well as sovereign shelters. Providing more than just a fish/shelter to those in need, instead providing fishing/building tools & knowledge of how to use them that will provide for their needs over a lifetime.
At the same time, by training local craftsmen with on-the-job vocational technology education the tools and skills necessary for establishing e
ssential infrastructure for cottage industry that build cottages for local community members. By doing so we can minimize upfront capital costs, lower environmental impact, and contribute to empowering community members with right livelihood, as well as sovereign shelters. Providing more than just a fish/shelter to those in need, instead providing fishing/building tools & knowledge of how to use them that will provide for their needs over a lifetime. To be sovereign means to not have to ask anyone. This CAN be accomplished by dealing with all waste onsite, collecting and properly disposing of your solid and liquid waste onsite, by generating, storing, and distributing power locally. By being able to Do The Work yourself, fund the build yourself, and be responsible for the results yourself reliance on outsourced specialists is avoided. Asking insurance agents, zoning/code officers, and finance officers to manage risk, to permit your designs, and to fund your shelter with fiat debt-notes is to become a “House Slave”, living in over-priced, badly built, gilded cages designed for profit, not to cultivate quality of life for all on it.
To be sovereign means to not have to ask anyone. This CAN be accomplished by dealing with all waste onsite, collecting and properly disposing of your solid and liquid waste onsite, by generating, storing, and distributing power locally. By being able to Do The Work yourself, fund the build yourself, and be responsible for the results yourself reliance on outsourced specialists is avoided. Asking insurance agents, zoning/code officers, and finance officers to manage risk, to permit your designs, and to fund your shelter with fiat debt-notes is to become a “House Slave”, living in over-priced, badly built, gilded cages designed for profit, not to cultivate quality of life for all on it.Current compliance, finance, and insurance infrastructure, when combined with the inflexible, design, and construction processes cannot help but build "dead structures". Not designed for, adapted to, or adapted by the inhabitants, our built environments do not truly support their inhabitants or the external environment they're dropped into. An entirely new paradigm, a "Livingry Design/Build/Operate" science and art of cultivated curated living systems is how these mistakes can be remedied going forward.
Biodome Igloos: designed as basic 'cellular units and family 'tissues' coordinating operations to form multi-species community 'organisms'. Using good design, conscious cultivation, and responsible stewardship to customize stacked living systems out of community curated patterns and transformative process IS how we heal all our relations** by healing ourselves with food as medicine, right livelihood for value-added services, and mathematics to fabricate trust and establish truth.
Decentralized, closed-loop, off-grid, owner-built residential 'nodes' that are manufactured with local materials and readily available tools enables this for more of humanity than ever before.
The unique recipe of patterns curated from centuries of ideas in order to enable all this includes:
- Custom designed on-site manufacturing enabled by modern 3d printing technology controls supply chain risks while providing flexibility in sizing, geometry, and the types of framing elements used https://www.thingiverse.com/thing:6244858/files
- Latex cement canvas, thin-shell cement custom coverings using “waste” paint diverted from the landfills https://www.instructables.com/Latex-Concrete-Roof/ & https://www.amazon.com/gp/product/1412039975/ref=as_li_ss_tl
- Japanese Shou Sugi Ban wood burning treatment avoids chemical off-gassing from wood preservatives to create beautiful rot, termite, and fire resistant wood framing elements http://www.ShouSugiBan.com
- Space age ceramic insulative paint additives designed for space shuttle tiles and commonly used to insulate yurts and RVs https://thermoshield.com/ & https://hytechsales.com/thermacels-insulating-additive-bulk
- Applying the thin-shell canvas cement to the flooring, over a typical earthen floor base of gravel and sand, avoids the expense in materials and labor of building a pier & beam deck or pouring a traditional cement slab
- Using re-pelletized Styrofoam as an insulative aggregate in the curtain walls as in-fill between the steel and wood structural elements brings additional sound and weatherproofing to the vertical walls, while diverting more waste from the landfills. https://youtu.be/nwv10Y9GBiQ?si=BJmMCWsKl_u9aFYX
- Mass manufacturing of metal trampolines brings economies of scale and diversion of unused waste from recycling streams delivered with durable, strong, pre-fabricated wall, footing, and perimeter beam framework.
- The simple Igloo shaped framework and lightweight framing/skinning elements creates an infinite variety of grouping together to create additional indoor and outdoor living, working, and playing areas that can grow organically as needs change and evolve, and can easily be modified for cold weather and/or tropical climates, as well as sand, rock, or even flood plain and water top foundations.
The biggest design/build challenges were how to reach the topmost area of the roof to apply the paint, cement, and insulation to weatherproof the canvas as the Gradual Stiffening application enables only limited self-scaffolding, without having to rent expensive lifts or build scaffolding and how to safely and effectively connect the dome hemisphere to the perimeter beam at the top of the trampoline oreo walls.
Leaving the 5 triangular dormer-style clerestory window openings until last made reaching uppermost surfaces possible. Purchasing a 12” compound bevel sliding chop saw allowed use of a 2”x12” shelf as the transition between the steel perimeter beam and the dome hemisphere. The challenge of securing the canvas to the steel framing elements was solved by using roofing screws to attach thin wood strips where needed. Not going with the stain grade finish wood would’ve allowed for use of an airless paint sprayer to lower the labor costs and use of a mortar sprayer will speed up the application of the latex cement mud mixture to the canvas. Use of removable slip forms, can allow for foam-crete wall in-fill to insulate against temperature and sound around the ground floor vertical walls.
The result of this is true Home Ownership, in the form of an ‘idea’ that cannot be taken, doesn’t need to be financed or permitted, and provides sustainable, healthy, living habitats for ourselves, our families and businesses.
BioDome Igloo Feature Stack:
-
- Humanure Nightsoil/Nitrogen Collector
-
- BSFL cultivator
-
- 50 sq ft Grey water wicking bed garden
-
- 50 sq ft Black water wicking bed
-
- 100 sq ft, spiral herb, aquaponics, overflow wicking bed garden
-
- Methane/Nat Gas generating above ground septic bag
-
- Nat Gas stove/H2O Heater
-
- BTC Mining Spaces Heater/Clothes Dryer
-
- Indoor/Outdoor Showers
-
- Kitchen/Bath sinks
-
- Greywater Clothes Washer
-
- BioSand/3-stage/UV Light filter & disinfection
-
- On-demand water pump
-
- ~850 gal rain tanks
-
- Fridge/Freezer
-
- desks/couch/TV/platform bed
-
- 3 ext. doors & 2 int. pocket doors
-
- Solar array, charger, inverter, & batteries
-
- Passive Solar H2O Heater
-
- Indirect lighting & natural ventilation
-
- 17 windows
-
- MgO “cerama-crete”
-
- Rocket Cob Oven
-
- 2 burner cinderblock wood stove
-
- Vermiculture worm chute/bins
-
- 72 sq ft garden porch
-
- 120 sq ft utility courtyard
-
- 200 sq ft ground floor climate controlled space
-
- 64 sq ft 2nd story floor space
-
- 200-500 sq ft rainwater catching roof & awnings
Achieved with modular adaptability, expandability, & scalability, with readily available tools, materials, and skill sets.
BioDome Igloo Function Stack:
- Self-Finance & Self-Build/Maintain shelter for not only ourselves, families, and businesses, BUT, also for our tools, schools, & gardens.
- Sovereign control over the supply chains providing for universal daily needs of ALL the soil/plant/animal/human inhabitants:
- Food cultivation for the entire ecosystem from => worms, flys, fungi, H20/soil bacteria, chickens, tilapia, cats, dogs, & humans
- Water catchment, storage, & treatment for => gardens, fish, & animals
- Shelter for private possessions from => wind, rain, sun, animals, bugs, molds, fire, extreme temps, prying eyes, & sticky fingers
- Fuel for cooking, heating, drying, & charging from => wood, sun, biomass, & natural gas
- Power for electronic appliances/fixtures, AC, BTC mining => sun, wind, nat gas, & potentially, biomass, micro-hydro, and/or hydrogen upgrades.
- Waste management for solids, liquids, & gases from => flush toilets, compost bins, and septic tanks
- Money for labor costs, infrastructure upgrades, and property taxes from => BTC mining, short/mid/long term rental, savings from closed-loop food, power, water, & waste systems
- Empowering Trade Skills enabling immediate ‘Right Livelihood’ through locally offered design/build/maintenance service offerings provided to neighboring communities.
- Scalable Growth designed appropriately, efficiently, and sustainably, built & maintained by those using the infrastructure.

Skill share/shelter seeding in multiple communities through a Vocational Tech Building Blitz
More useful than a fishing pole, providing knowledge on how to manufacture multiple fishing rods, nets, & traps can empower new adopters at scale with a fire of knowledge that cannot be extinguished. Owner designed, built, and maintained small scale shelter can now truly be ‘Owned’ in a way that not only address international chronic housing shortages, while also lowering monthly food costs, 3-6 weeklong Building Blitz onsite intensives create the potential spreading tradecrafts offering right livelihood by providing putting the newly learned trade skills to use for the local community. Small, but beautiful residential housing/food production/resource management in a decentralized, affordable, and communicable form factor is necessary. Providing Pattern Language and Permaculture design strategies, tactics, and skills training on a curated design dictionary, tool, and material stack is only the beginning.
Train a man on how to shelter and feed himself and his family and you offer him the opportunity for reliable right livelihood by exercising those vocational crafts as a service offered to his neighbors in his local marketplace, too. Families, schools, churches, all can organize clustered Biodome Igloo Pattern Stacks to lower their monthly food, energy, and shelter costs.
Craftsmen education through a ‘Building Blitz’ can systemize the training of the crew leaders, who can themselves train more crew and team leads. Offering land owners and craftsmen/women the opportunity to assemble one pre-manufactured kit and build out two new kits to completion over 3-6 weeks depending on the simplicity or complexity of the project. Perhaps, all crew members working together on the 1st Biodome, then 2 teams splitting off to duplicate two more under supervision from scratch, space, budgets, and time allowing, with each team completing two more Biodomes without supervision (providing 5 residential ecosystems in total), in order to earn their Designer/Builder Certification.
Resulting in 3 completed BioDome Igloo Stack ecosystems and up to 3 newly certifiably trained Crew Leaders. Costs will vary greatly depending on local economics, supply chains, and labor markets, but this Invisible Structural Pattern may allow for internationally scalable Vocational Tech training that addresses food, housing, and employment shortages worldwide.
BioDome 5 Special Features lead to 1 Unique Result:
- 3D Printing: Free, open-sourced &/or DIY designed & locally manufactured custom structural brackets
- ASA plastic: mold, bug, UV, high temp, and impact resistant
- PETG plastic: mold, bug, UV, flexible & durable. Potentially, locally upcycled out of plastic bottles, but not as resistant to high temps
- Infinitely customizable and replicable
- Latex Concrete Habitat: Low-cost, adaptable, and effective thin shell cement/canvas/latex paint ‘skinning’ technique 1st developed in the 1970s
- Hard or Flexible as needed, adapting to any shape and multiple materials, with inexpensive tooling or training
- Easily adheres to wood, metal, or plastics with staples, paint, & cement, for both initial construction and ongoing repairs/additions
- Magnesium Oxide MgO Siding: Manufactured Non-toxic, inert, low-temp, paintable ceramic exterior & interior panels
- water, fire, mold, and bug resistant
- 50+ yr life span that adds thermal mass & soundproofing
- Thermoshield Paint: Borosilicate microspheres, a space-age insulative material designed for space shuttle re-entry, available as both an additive and pre-mix roofing/siding/wall paint
- Flexible waterproofing coat providing heat reflection equivilant to R20 insulation with only 1/8” coating
- Non-toxic, inert, ceramic beads available as premixed ‘Thermoshield’ potable roofing paint
- Trampoline ‘Oreo’ Framing:Flipped & stacked trampoline steel perimeter floor and wall beams, as well as load bearing poles
- Improved performance & lower cost by repurposing established steel trampoline mass-machining, packaging, and distribution infrastructure
- Use 1 ½” diameter galvanized steel tubing in low cost manufactured kits available wordwide, providing strength, durability, and light-weight efficiency at scale



‘Permit-less Design’:
The BioDome Igloo Pattern Stack creates a durable, duplicatable, scalable, and transmittable DIY residential design pattern dictionary, integrating abstract philosophical/mathematical ideas adapted from Geodesic Geometry, Bau Biology/Biomimicry/Biophilic design, Cryptography, Austrian Economics, Permaculture, Pattern Language, & Free Open-Source Software, with tangible physical infrastructure
- Built appropriately small & light-weight, with grown factored in, to collect, store, reduce, and reuse energy production and consumption in a macro-organism, a closed-loop intentionally planned, built, and managed living residential ecosystem
- Providing a full-stack, top-to-bottom vertical supply chain for ALL of a self-contained ecosystem’s essential daily needs
- Transforms consumption (i.e. trash) into production (i.e. treasure), accruing sustainable residual surplus capital in multiple form factors, H2O, KwHrs, Bug/Plant/Animal Inhabitants, Nat Gas, Satoshis, & Compute Power
- This idea is stacked on the shoulders of these well-known & unknown intellectual giants, as well as countless peers of the realm:
- Buchminster Fuller- ‘Critical Path’
- Bill Mollison- ‘Permaculture Design Manual’
- Christopher Alexander- ‘Pattern Language Design’
- Dr. Albert Knott & Dr. George Nez- ‘Latex Concrete Habitat’
- E. F. Shumacher- ‘Small Is Beautiful’
- Ayn Rand- ‘The Fountainhead’
- Satoshi Nakamoto- ‘The Bitcoin Whitepaper’
- And many more anonymous & known peers, mentors, and clients…
-
 @ 4520e45a:aa52208a
2025-03-24 20:26:56
@ 4520e45a:aa52208a
2025-03-24 20:26:56👾 Hash Obwohl ein Bitaxe mit 1TH eine Billion Hashes pro Sekunde generiert, werden nicht alle Hashes an den Pool übermittelt — das käme einer Dos-Attacke gleich, würde unnötig Bandbreite verschwenden und den Stratum-Pool-Server massiv belasten.
🏋️ Work-Difficulty Deshalb wird für jeden Worker eine individuelle Work-Difficulty festgelegt. Im Stratum-Protokoll, bekannt als <mining.set_difficulty>. Es werden also nur Shares übermittelt, welche grösser als die festgelegte Work-Difficulty sind.
💡 Um eine Share mit Difficulty 1 zu finden, muss ein Miner erwartungsgemäss 2³² = 4'294'967'296 = 4.29G Hashes generieren.
✉️ Share Wenn ein Hash alle notwendigen Kriterien erfüllt und die Nonce-Difficulty grösser ist als die vom Pool festgelegte Work-Difficulty, wird er als Share dem Pool übermittelt.
⏱️ Bei ckpool wird die Work-Difficulty für einen Worker so angepasst, dass im Durchschnitt 20 Shares pro Minute – also alle 3 Sekunden 1 Share – überliefert wird, das ergibt circa 1200 Shares/Stunde
⏱️ Bei Public Pool wird die Work-Difficulty für einen Worker so angepasst, dass im Durchschnitt 6 Shares pro Minute – also alle 10 Sekunden 1 Share – überliefert wird, das ergibt circa 360 Shares/Stunde
📡 Es geht dabei letztlich um die Kommunikation zwischen Miner und Pool, also konkret, wie oft pro Minute dein Miner Shares an den Pool übermittelt und wieviele Datenpakete gesendet/empfangen/verarbeitet werden müssen.
📈 5-20 Shares pro Minute ergeben auch eine einigermassen aussagekräftige Hashrate, damit stets überprüft werden kann, ob dein Miner korrekt arbeitet.
⛏️ Ob Miner pro Minute 20 Shares mit jeweils einer Nonce-Difficulty von 600 an den Pool übermittelt und Miner pro Minute nur 6 Shares dafür jeweils mit einer Nonce-Difficulty von 2000 an den Pool übermittelt ist am Ende das gleiche.
💪 Beide haben die identische Arbeit geleistet (20×600 = 6×2000 = 12'000×1), nur dass der eine 'viele einfache' und der andere 'wenige schwierige' Shares übermittelt hat.
-
 @ 866e0139:6a9334e5
2025-03-24 19:48:43
@ 866e0139:6a9334e5
2025-03-24 19:48:43Autor: Philipp Mattheis. Dieser Beitrag wurde mit dem Pareto-Client geschrieben und erschien zuerst auf dem Substack-Blog "BlingBling". Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier.**
800 Milliarden Euro will die EU ausgeben, um die Ukraine und den Kontinent in ein “stählernes Stachelschwein” zu verwandeln. Deutschland selbst will künftig Verteidigungsausgaben aus der Schuldenbremse ausnehmen, was nichts anderes als eine unbegrenzte Kreditlinie für das Militär bedeutet. Hinzu kommt ein “Sondervermögen” in Höhe von 500 Milliarden Euro für Infrastruktur. Das klingt nach einem Spartopf, den man für schwere Zeiten angelegt hat. Es soll die Tatsache verschleiern, dass es sich dabei um Schulden handelt. Der vermutlich baldige Kanzler Friedrich Merz bricht damit sein Wahlversprechen, die Schuldenbremse einzuhalten. Beschließen soll das Paket noch ein abgewählter Bundestag, da im neuen wohl die Mehrheit fehlt.
Frisches Geld für Krieg und Aufrüstung
Womit also ist zu rechnen, wenn demnächst fast eine Billion frisch gedruckte Euro in Drohnen, Panzer und Raketen investiert werden?

Das beste Beispiel der jüngeren Geschichte ist China: 2009 legte die chinesische Regierung das bisher größte Infrastrukturprojekt der Welt in Höhe von 440 Milliarden Euro auf. Finanziert wurde es durch günstige Kredite, die vor allem an Staatsunternehmen vergeben wurden. Nachdem die Welt nach der in den USA ausgelösten Immobilienkrise 2008 in die Rezession gerutscht war, „rettete“ dieses Paket die globale Konjunktur. China hatte zu diesem Zeitpunkt großen Bedarf an Flughäfen, Straßen und vor allem Zügen. Das Paket war riskant: Schier unbegrenztes Geld, das begrenzten Waren hinterherjagt, führt zu Inflation. Billige Kredite führen meist dazu, dass Unternehmen nicht mehr effizient wirtschaften, und Schuldenberge vor sich her wälzen.
Allerdings wurde das Geld in Produktivität investiert. Denn wenn Menschen und Waren einfacher reisen können, nimmt die Geschäftstätigkeit zu: Arbeitnehmer werden mobiler, Unternehmen konkurrenzfähiger, die Preise sinken. Die Investitionen lohnen sich also, weil sie zu mehr Wirtschaftswachstum führen. Vereinfacht gesagt: Die Schulden können zurückgezahlt werden, und am Ende bleibt noch mehr übrig. In diesem Fall führen Schulden nicht zu Inflation: Durch die gesteigerte Produktivität stehen jetzt sogar mehr Waren der Geldmenge gegenüber.
15 Jahre später kämpft die zweitgrößte Volkswirtschaft zwar noch immer mit den Problemen, die aus diesem Paket resultieren - die Immobilienkrise ist eine indirekte Folge davon. Trotzdem war das Programm ein Erfolg: die Städte, Flughäfen und vor allem Zugstrecken führten zu einer höheren wirtschaftlichen Aktivität oder Produktivität. China ist heute ein wesentlich moderneres Land als vor dem Paket, und verfügt über modernste und größte Netz aus Hochgeschwindigkeitszügen der Welt. Neue Schulden können positiv sein - wenn das Geld produktiv investiert wird.
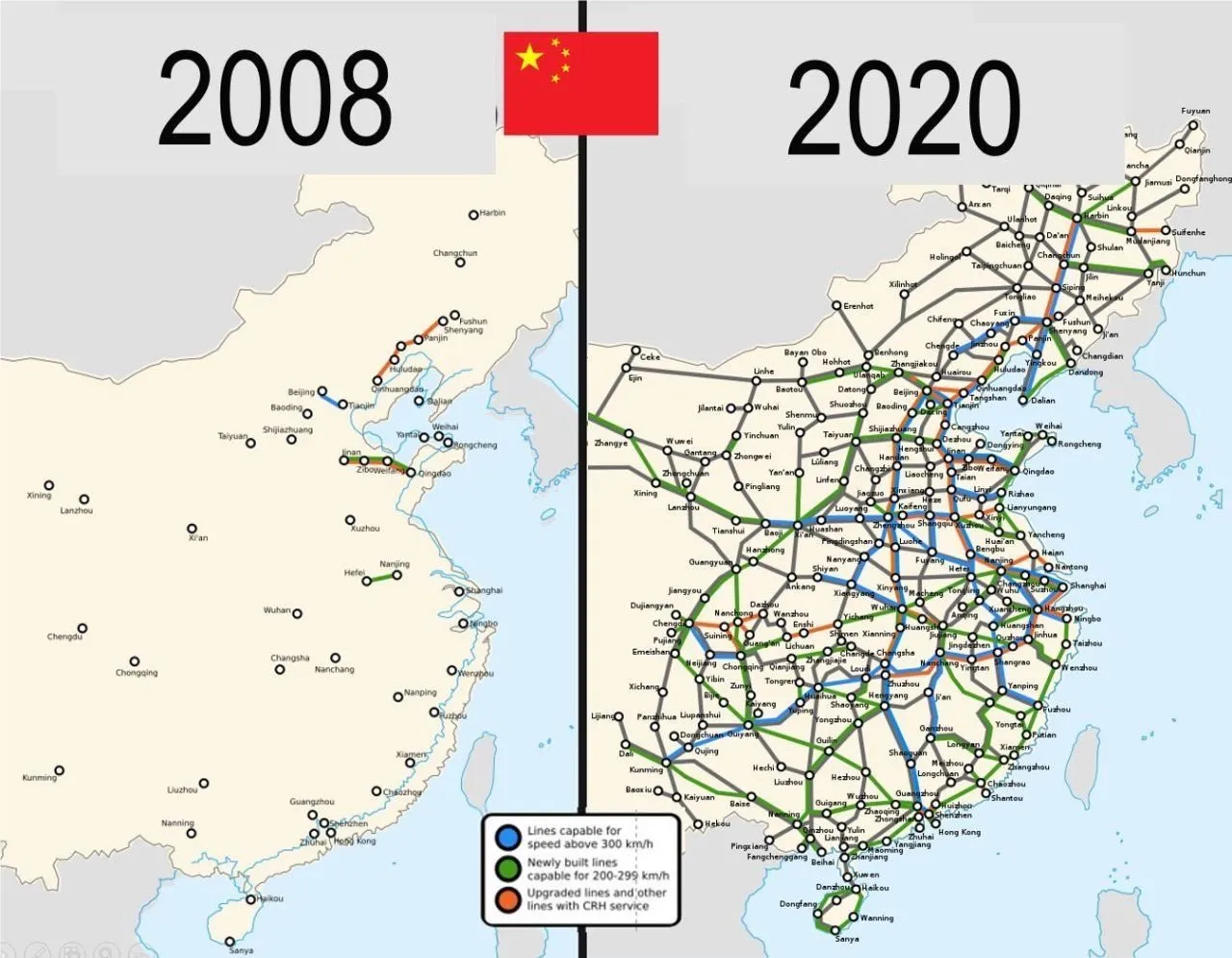
Auch in Europa lassen sich mit dem Geld-Paket zunächst mehrere Probleme auf einmal lösen: Deutschland ist noch immer ein Industriestandort mit hohen Produktionskapazitäten. Werke der Auto- und Zulieferindustrie können theoretisch zur Waffenproduktion umfunktioniert werden. Immer noch besser als sie stillzulegen oder an die Chinesen zu verkaufen, werden viele Kommentatoren schreiben.
Allein in der deutschen Automobil-Zulieferindustrie sind im vergangenen Jahr über 19000 Arbeitsplätze verloren gegangen. Viele von den Entlassenen können nun Arbeit in der Rüstungsindustrie finden. Oder wie Hans Christoph Atzpodien, Hauptgeschäftsführer des Bundesverbandes der Deutschen Sicherheits- und Verteidigungsindustrie in der WirtschaftsWoche sagt:
„Das Motto muss lauten: Autos zu Rüstung! Anstatt einen volkswirtschaftlichen Schaden durch den Niedergang der Auto-Konjunktur zu beklagen, sollten wir versuchen, Produktionseinrichtungen und vor allem Fachkräfte aus dem Automobilsektor möglichst verträglich in den Defence-Bereich zu überführen“
Immerhin: ein großer Teil des Geldes soll auch in Infrastrukturprojekte fließen: Brücken, Bahn, Internetausbau. Deutschland, und damit Europa, wird in den kommenden Monaten also eine große Party feiern, die über die Tatsache hinwegtäuschen wird, dass man einen dummen Krieg verloren hat. In den kommenden Monaten werden sich Verbände und Organisationen um das Geld reißen. Das Geld wird ein auch kollektiv-psychologisches Ventil sein, um das eigene Versagen bei Corona, Klima und Ukraine vergessen zu machen.
Es gibt allerdings einen wesentlichen Unterschied zum chinesischen Stimulus-Paket 2009: Rüstungsgüter sind im Gegensatz zu Zugstrecken totes Kapital. Eine neue Drohne oder Panzer führt nicht zu mehr Produktivität, im Gegenteil: Kommen sie zum Einsatz, zerstören sie Brücken, Häuser, Straßen und töten Menschen. Die Produktivität sinkt also. Im besten Fall kann Militärgerät herumstehen und vor sich hin rosten. Auch dann aber ist es „totes Kapital“, das nichts zur Produktivität beiträgt. Kommt es zum Einsatz, stehen der nun verringerten Warenmenge eine noch größere Geldmenge gegenüber. Die Inflation steigt.
DIE FRIEDENSTAUBE JETZT ABONNIEREN:
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel in Ihr Postfach, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht).
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):
Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: milosz@pareto.space oder kontakt@idw-europe.org.
Schleichende Militarisierung
Auch gesellschaftlich wird das Paket mit seinem Blanko-Scheck für die Verteidigungsindustrie viel verändern: Es kommt zu einer „Eichung“ der Gesellschaft, eine kollektive Abscheu des gemeinsamen Feindes. Scharfmacher, eigentlich mittelmäßiger Akademiker und Bürokraten, wie Carlo Masala und Claudia Major werden eine noch größere Rolle im öffentlichen Diskurs spielen und die Talkshows dominieren, die von einer immer älter werdenden deutschen Bevölkerung geglotzt werden. Abweichende Meinungen auf Online-Plattformen zensiert, unter dem Vorwand, die Demokratie sei in Gefahr
Da die Rüstungsindustrie dann eine wichtigere Rolle für die Gesamtwirtschaft spielt, wird ihr Einfluss auf die Politik in Form von Lobbyisten und Verbänden zunehmen. Politiker merken schnell, dass sie von der medialen Aufmerksamkeitsökonomie nach oben gespült werden, wenn sie immer radikalere Forderungen stellen. So empfahl der ehemalige Außenminister Joschka Fischer die Woche die Wiedereinführung der Wehrpflicht für Männer und Frauen. “Star-Ökonomin” Isabella Weber will die Kriegswirtschaft mitplanen.
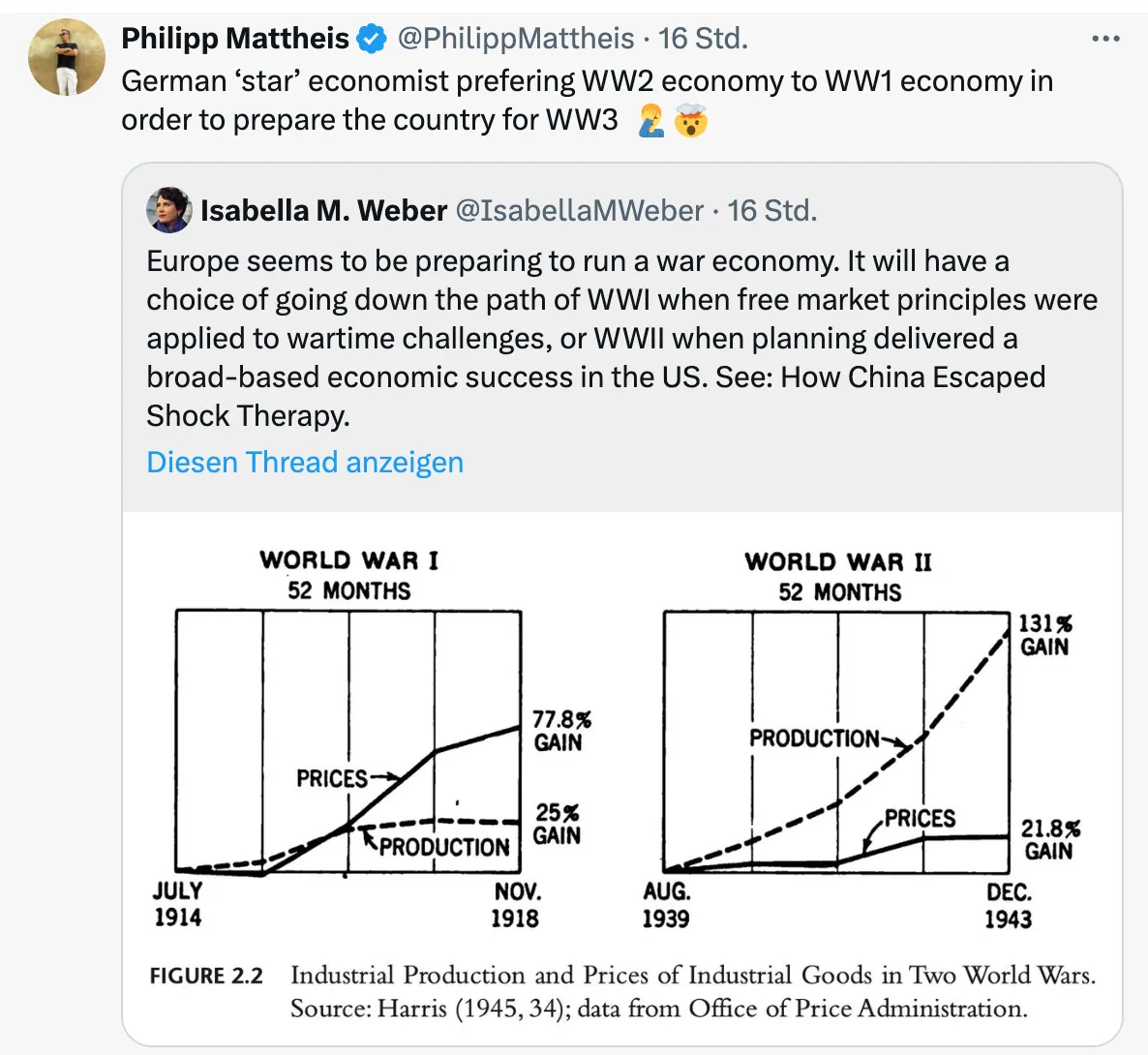
Der Kontinent wird sich langsam wandeln von einem „Friedensprojekt“ zu einem „metallenen Stachelschwein“, ergo Kriegsprojekt, denn ohne dämonisierten Feind funktioniert das Programm nicht. Der Ton wird rauer, autoritärer, und die Meinungsfreiheit weiter eingeschränkt werden. Die seit 2020 eingeführten Werkzeuge zur soften Propaganda („kognitive Kriegsführung”) werden verfeinert und ausgebaut werden, sodass weiterhin 80 Prozent der Bevölkerung alle noch so antihumanen Maßnahmen gutheißen werden.
Und dann?
Wie Julian Assange einmal sagte: “Das Ziel ist kein erfolgreicher Krieg. Das Ziel ist ein endloser Krieg.” Der Konflikt muss weitergehen, ewig schwelen oder ein neuer gefunden werden, da sonst ein Teil der Wirtschaftsleistung kollabiert.
Nach ein, zwei oder auch erst drei Jahren, werden erste Probleme sichtbar. Die Party endet, der Kater setzt langsam ein. Die Finanzierung an den Kapitalmärkten wird für Deutschland immer kostspieliger. Der Schuldendienst wird einen größeren Teil des Haushalts einnehmen. Die Bürger müssen dies mitfinanzieren. Der voraussichtlich neue Bundeskanzler Friedrich Merz sprach bereits von der „Mobilisierung der deutschen Sparguthaben“.

Was im Ersten Weltkrieg „Kriegsanleihen“ hieß, wird einen schickeren Namen bekommen wie „olivgrüne Bonds“. You name it. Alternativ lässt sich ein Verteidigungs-Soli einführen, oder das Kindergeld streichen, wie kürzlich Ifo-Chef Clemens Fuest forderte.
Philipp Mattheis, Jahrgang 1979, ist München-Korrespondent der WiWo und betreibt den Substack-Blog "BlingBling". Er studierte Philosophie und absolvierte die Deutsche Journalistenschule. Von 2012 bis 2015 war er in Shanghai als China-Korrespondent der WiWo tätig. Von 2016 bis 2020 berichtete er aus Istanbul. Mattheis ist Autor mehrere Bücher zu, China, Geo-, und Wirtschaftspolitik. www.philippmattheis.com
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 2e8970de:63345c7a
2025-03-24 18:40:58
@ 2e8970de:63345c7a
2025-03-24 18:40:58As Congress gears up to pass President Trump’s massive legislative package, one of the biggest fights is over the future of Medicaid. To make their targeted budget numbers, Republicans will likely need to carve hundreds of billions of dollars in spending out of the health program that serves lower-income people. But Medicaid is a political flashpoint because of the core role it plays in the lives of millions of Americans—many of whom vote for Republicans—as well as state budgets and the healthcare economy.
https://www.wsj.com/politics/policy/medicaid-cuts-health-insurance-in-charts-56962433?mod=hp_lead_pos7
originally posted at https://stacker.news/items/923851
-
 @ 6e0ea5d6:0327f353
2025-02-21 18:15:52
@ 6e0ea5d6:0327f353
2025-02-21 18:15:52"Malcolm Forbes recounts that a lady, wearing a faded cotton dress, and her husband, dressed in an old handmade suit, stepped off a train in Boston, USA, and timidly made their way to the office of the president of Harvard University. They had come from Palo Alto, California, and had not scheduled an appointment. The secretary, at a glance, thought that those two, looking like country bumpkins, had no business at Harvard.
— We want to speak with the president — the man said in a low voice.
— He will be busy all day — the secretary replied curtly.
— We will wait.
The secretary ignored them for hours, hoping the couple would finally give up and leave. But they stayed there, and the secretary, somewhat frustrated, decided to bother the president, although she hated doing that.
— If you speak with them for just a few minutes, maybe they will decide to go away — she said.
The president sighed in irritation but agreed. Someone of his importance did not have time to meet people like that, but he hated faded dresses and tattered suits in his office. With a stern face, he went to the couple.
— We had a son who studied at Harvard for a year — the woman said. — He loved Harvard and was very happy here, but a year ago he died in an accident, and we would like to erect a monument in his honor somewhere on campus.— My lady — said the president rudely —, we cannot erect a statue for every person who studied at Harvard and died; if we did, this place would look like a cemetery.
— Oh, no — the lady quickly replied. — We do not want to erect a statue. We would like to donate a building to Harvard.
The president looked at the woman's faded dress and her husband's old suit and exclaimed:
— A building! Do you have even the faintest idea of how much a building costs? We have more than seven and a half million dollars' worth of buildings here at Harvard.
The lady was silent for a moment, then said to her husband:
— If that’s all it costs to found a university, why don’t we have our own?
The husband agreed.
The couple, Leland Stanford, stood up and left, leaving the president confused. Traveling back to Palo Alto, California, they established there Stanford University, the second-largest in the world, in honor of their son, a former Harvard student."
Text extracted from: "Mileumlivros - Stories that Teach Values."
Thank you for reading, my friend! If this message helped you in any way, consider leaving your glass “🥃” as a token of appreciation.
A toast to our family!
-
 @ bf95e1a4:ebdcc848
2025-03-24 17:14:48
@ bf95e1a4:ebdcc848
2025-03-24 17:14:48This is a part of the Bitcoin Infinity Academy course on Knut Svanholm's book Bitcoin: Sovereignty Through Mathematics. For more information, check out our Geyser page!
Everything A Trade
All human interaction can be defined as trade. Yes, all human interaction. Every time a human being interacts with another, an exchange takes place. In every conversation we have, we exchange information with each other. Even the most trivial information is of some value to the other person. If information didn’t have any value to us, we wouldn’t talk to each other. Either what the other person says is valuable to us, or we find it valuable to give information to them. Oftentimes both. At the core of all human interaction that isn’t violent, both parties perceive that they gain some value from it, otherwise the interaction wouldn’t have taken place at all. Civilizations begin this way — two people finding it valuable to interact with each other. That’s all it takes.
So, what constitutes value? What we find valuable is entirely subjective. A comforting hug, for example, probably has a different value to a two-year-old than it has to a withered army general. Even the most basic action, such as breathing, encapsulates the whole value spectrum. We tend to forget that even a single breath of air can be of immense value to us under the right circumstances. A single breath is worth more than anything on the planet to a desperate free-diver trapped under ice, while worth nothing to a person with a death wish in clean forest air on a sunny summer day. Value is derived from supply and demand, and demand is always subjective. Supply is not.
Since all of our lives are limited by time, time is the ultimate example of a scarce, tradeable resource. We all sell our time. We sell it to others, and we sell it to ourselves. Everyone sells their time, either through a product that took them a certain amount of time to produce, or as a service, and services always take time. If you’re an employee on a steady payroll, you typically sell eight hours of your day, every day, to your employer. If you’re doing something you truly love to do, that eight-hour day still belongs to you, in a way, since you’re doing what you’d probably be doing anyway if you had been forced to do it for free. Sometimes, we sacrifice time in order to acquire something in the future. An education, for instance, gives no immediate reward but can lead to a better-paying, more satisfying job in the future. An investment is basically our future self trading time with our present self at a discount. Once again, every human interaction viewed as trade.
It’s rooted in physics. For every action, there is an equally large reaction. Trade is at the very core of what we are, and the tools we use to conduct trade matter a lot to the outcome of each transaction. Money is our primary tool for expressing value to each other and if the creation of money is somewhat corrupt or unethical, that rot spreads down throughout society, from top to bottom. Shit flows downhill, as the expression goes.
So what is money, or rather, what ought money to be? In order for two persons to interact when a mutual coincidence of needs is absent, a medium of exchange is needed in order to execute a transaction. A mutual coincidence of needs might be “You need my three goats, and I need your cow,” or even “both of us need a hug.” In the absence of a physical good or service suitable for a specific transaction, money can fulfill the role of a medium of exchange. What most people fail to realize is that the value of money, just as the value of everything else, is entirely subjective. You don’t have to spend it. The problem with every incarnation of money that mankind has ever tried is that its value always gets diluted over time due to inflation in various forms. Inflation makes traditional money a bad store of value, and money needs to be a good store of value in order to be a good investment, or in other words, a good substitute for your time and your effort over time. Bitcoin tries to solve this problem by introducing absolute scarcity to the world, a concept that mankind has never encountered before. To comprehend what such a discovery means for the future, one needs to understand the fundamentals of what value is and that we assign a certain value to everything we encounter in life, whether we admit it or not. In short, we assign value to everything we do, value is derived from supply and demand, and supply is objective while demand is subjective.
Free trade emerges out of human interaction naturally and it is not an idea that was forced upon us at any specific point in time. The idea that markets should be regulated and governed, on the other hand, was. Free trade is just the absence of forceful interference in an interaction between two humans by a third party. There’s nothing intrinsically wrong or immoral about an exchange of a good or service. Every objection to this is a byproduct of the current global narrative — a narrative that tells us that the world is divided into different nations and that people in these nations operate under various sets of laws, depending on what jurisdiction they find themselves in. All of these ideas are man-made. No species except humans does this to themselves. Animals do trade, but they don’t do politics.
Bitcoin and the idea of truly sound, absolutely scarce money inevitably make you question human societal structures in general and the nature of money in particular. Once you realize that this Pandora’s box of an idea can’t be closed again by anyone, everything is put into perspective. Once you realize that it is now possible for anyone with a decently sized brain to store any amount of wealth in that brain or to beam wealth anonymously to any other brain in the world without anyone else ever knowing, everything you were ever told about human society is turned on its head. Everything you thought you knew about taxes, social class, capitalism, socialism, economics, or even democracy falls apart like a house of cards in a hurricane. It is, in fact, impossible to comprehend the impact Bitcoin will have on the planet without also understanding basic Austrian economics and what the libertarian worldview stems from.
Imagine growing up in an Amish community. Until your sixteenth birthday, you’re purposely completely shielded off from the outside world. Information about how the world really works is very limited to you since internet access, and even TVs and radios, are forbidden within the community. Well, from a certain perspective, we’re all Amish. How money really works is never emphasized enough through traditional media or public educational institutions. Most people believe that the monetary system is somehow sound and fair when there’s overwhelming evidence to the contrary all over the globe. Ask yourself, do you remember being taught about the origins of money in school? Me neither. I don’t believe that there’s some great, global conspiracy behind the fact that the ethics of money creation isn’t a school subject, but rather that plain old ignorance is to blame for the lack of such a subject primarily. As soon as their math-skill limit is reached, people seem to stop caring about numbers. The difference between a million and a billion seems lost on a depressingly large part of the world's population. In the chapters ahead, we’ll explore the pitfalls of central banking, how money pops into existence, and how inflation keeps us all on a leash.
About the Bitcoin Infinity Academy
The Bitcoin Infinity Academy is an educational project built around Knut Svanholm’s books about Bitcoin and Austrian Economics. Each week, a whole chapter from one of the books is released for free on Highlighter, accompanied by a video in which Knut and Luke de Wolf discuss that chapter’s ideas. You can join the discussions by signing up for one of the courses on our Geyser page. Signed books, monthly calls, and lots of other benefits are also available.
-
 @ 57d1a264:69f1fee1
2025-03-24 17:08:06
@ 57d1a264:69f1fee1
2025-03-24 17:08:06Nice podcast with @sbddesign and @ConorOkus about bitcoin payments. https://www.youtube.com/watch?v=GTSqoFKs1cE
In this episode, Conor, Open Source product manager at Spiral & Stephen, Product Designer at Voltage & Co founder of ATL Bitlab join Stephan to discuss the current state of Bitcoin user experience, particularly focusing on payments and the challenges faced by users. They explore the comparison between Bitcoin and physical cash, the Western perspective on Bitcoin payments, and the importance of user experience in facilitating Bitcoin transactions.
They also touch upon various payment protocols like #BOLT11, #LNURL, and #BOLT12, highlighting the need for interoperability and better privacy features in the Bitcoin ecosystem. The discussion also covers resources available for developers and designers to enhance wallet usability and integration.
@StephanLivera Official Podcast Episode: https://stephanlivera.com/646
Takeaways
🔸Bitcoin has excelled as a savings technology. 🔸The payments use case for Bitcoin still needs improvement. 🔸User experience is crucial for Bitcoin adoption. 🔸Comparing Bitcoin to cash highlights privacy concerns. 🔸Western users may not see a payments problem. 🔸Regulatory issues impact Bitcoin payments in the West. 🔸User experience challenges hinder Bitcoin transactions. 🔸Different payment protocols create compatibility issues. 🔸Community collaboration is essential for Bitcoin's future. 🔸Improving interoperability can enhance Bitcoin payments. Wallet compatibility issues can create negative user impressions. 🔸Designers can significantly improve wallet user experience. 🔸Testing compatibility between wallets is essential for user satisfaction. 🔸Tether's integration may boost Bitcoin adoption. 🔸Developers should prioritize payment capabilities before receiving capabilities. 🔸Collaboration between designers and developers can lead to better products. 🔸User experience improvements can be low-hanging fruit for wallet projects. 🔸A global hackathon aims to promote miner decentralization. 🔸Resources like BOLT12 and the Bitcoin Design Guide are valuable for developers. 🔸Engaging with the community can lead to innovative solutions.
Timestamps
(00:00) - Intro (01:10) - What is the current state of Bitcoin usage - Payments or Savings? (04:32) - Comparing Bitcoin with physical cash (07:08) - What is the western perspective on Bitcoin payments? (11:30) - Would people use Bitcoin more with improved UX? (17:05) - Exploring payment protocols: Bolt11, LNURL, Bolt12 & BIP353 (30:14) - Navigating Bitcoin wallet compatibility challenges (34:45) - What is the role of designers in wallet development? (43:13) - Rumble’s integration of Tether & Bitcoin; The impact of Tether on Bitcoin adoption (51:22) - Resources for wallet developers and designers
Links:
• https://x.com/conorokus • https://x.com/StephenDeLorme • https://bolt12.org/ • https://twelve.cash/ • https://bitcoin.design/guide/ • Setting Up Bitcoin Tips for Streamers](/watch?v=IWTpSN8IaLE)
originally posted at https://stacker.news/items/923714
-
 @ 4857600b:30b502f4
2025-02-20 19:09:11
@ 4857600b:30b502f4
2025-02-20 19:09:11Mitch McConnell, a senior Republican senator, announced he will not seek reelection.
At 83 years old and with health issues, this decision was expected. After seven terms, he leaves a significant legacy in U.S. politics, known for his strategic maneuvering.
McConnell stated, “My current term in the Senate will be my last.” His retirement marks the end of an influential political era.
-
 @ 401014b3:59d5476b
2025-03-24 16:34:24
@ 401014b3:59d5476b
2025-03-24 16:34:24Alright, hoops degenerates, it’s March 24, 2025, and we’re deep in the March Madness grinder—Sweet 16 time, baby! The bracket’s a damn battlefield, with Auburn, Michigan, Texas Tech, Arkansas, and Purdue locked in alongside some heavy hitters and sneaky upstarts. We’re breaking down every matchup, throwing out some ballsy picks, and calling the full Elite Eight squads on the road to San Antonio. This ain’t some nerdy chalk fest—let’s get loud, let’s get rowdy, and let’s see who’s got the stones to survive this chaos. Strap in, fam—here we go!
South Region: Auburn’s Warpath or Spartan Magic?
Auburn vs. Michigan
Auburn’s the SEC beast, shredding Creighton 82-70 with Tahaad Pettiford’s bench juice (14 points) and Johni Broome’s paint dominance (22 points, 10 boards). Michigan’s Big Ten scrappers outlasted Texas A&M 91-79—Dusty May’s got ‘em humming with Olivier Nkamhoua’s 18 points. The Tigers are a top-5 offensive team, but Michigan’s been scrappy, winning close games all season. Auburn’s depth and Broome’s interior game (top-10 in blocks) overpower Michigan’s grit—Auburn rolls, 78-71.
Ole Miss vs. Michigan St.
Ole Miss’s Chris Beard-led crew topped Iowa St. 91-78—Sean Pedulla dropped 20, and their top-30 offense is humming. Michigan St. beat New Mexico 71-63—Tom Izzo’s Spartans are battle-tested, with a top-15 defense (per KenPom). Ole Miss can score, but Sparty’s physicality (top-10 in defensive rebounds) and Izzo’s March magic (five Final Fours) shut ‘em down—Michigan St. grinds it, 74-69.
Elite Eight Matchup: Auburn vs. Michigan St.
West Region: Houston’s Clamps or Gators’ Grit?
Houston vs. Purdue
Houston’s D suffocated Gonzaga 81-78—L.J. Cryer dropped 22, and their top-5 defense (forcing 16 turnovers per game) is a nightmare. Purdue crushed San Diego St. 76-62—Braden Smith dished 15 assists, and Fletcher Loyer had 18. Cougars are elite defensively, but Purdue’s size (top-10 in offensive rebounds) and tempo keep it close. Houston’s clamps and Cryer’s clutch shooting (40% from three) edge it—Houston dominates, 70-66.
Florida vs. Maryland
Florida stunned UConn 77-75—Walter Clayton Jr.’s 10 points in a three-minute span sealed it. Maryland’s buzzer-beater over Colorado St. 72-71—Derik Queen’s heroics—got ‘em here. Gators are rolling (SEC tourney champs), but Maryland’s Crab Five (top-20 offense) and Queen’s clutch play (20 PPG in March) keep it tight. Florida’s depth (four starters averaging 12+ PPG) pulls through—Florida wins, 82-78.
Elite Eight Matchup: Houston vs. Florida
Midwest Region: Arkansas’ Chaos or Bama’s Firepower?
Texas Tech vs. Arkansas
Calipari’s Razorbacks punked St. John’s 75-66—DJ Wagner dropped 16, and their depth shone. Texas Tech’s Big 12 muscle crushed Drake 77-64—Darrion Williams had 28. Hogs’ talent (six guys in double figures vs. St. John’s) faces Tech’s balanced attack (top-25 offense). Arkansas’ chaos and Calipari’s March pedigree (four Final Fours) overwhelm—Arkansas storms, 82-77.
BYU vs. Alabama
BYU’s hot streak topped Wisconsin 91-89—Trevor Knell hit six threes, averaging 18.9 PPG in their nine-game win streak. Alabama blitzed Saint Mary’s 86-80—Mark Sears dropped 25. Cougars’ offense (top-10 in three-point shooting) meets Bama’s firepower (top-15 in offensive efficiency). Alabama’s speed and Sears’ scoring (21 PPG) edge it—Alabama wins, 88-84.
Elite Eight Matchup: Arkansas vs. Alabama
East Region: Duke’s Flagg Show or Cats’ Revenge?
Duke vs. Arizona
Flagg’s back—Duke crushed Baylor 89-86, with Flagg dropping 20 and 8. Arizona blitzed Oregon 87-83—Caleb Love had 27. Flagg’s versatility (top-5 defensive efficiency for Duke) faces Love’s scoring (20 PPG in March). Duke’s depth (six guys scoring 10+ vs. Baylor) and Flagg’s two-way play edge it—Duke flexes, 85-76.
Kentucky vs. Tennessee
Kentucky beat Illinois—Mark Pope’s Wildcats are 2-0 against Tennessee this season. Tennessee topped UCLA 72-67—Zakai Zeigler had 18 and 8 assists. Cats’ resilience (top-20 offense) meets Vols’ defense (top-15 efficiency). Kentucky’s Quad 1 wins (12 this season) and Pope’s game plan edge it—Kentucky wins, 82-78.
Elite Eight Matchup: Duke vs. Kentucky
Elite Eight Teams (Full List)
South: Auburn, Michigan St.
West: Houston, Florida
Midwest: Arkansas, Alabama
East: Duke, Kentucky
The Final Buzzer
Sweet 16’s a bloodbath, and the Elite Eight’s set—Auburn, Michigan St., Houston, Florida, Arkansas, Alabama, Duke, and Kentucky are my picks to keep dancing. SEC’s got seven teams in the Sweet 16, blue bloods are flexing, and mid-majors are toast. Hit me on Nostr if you disagree, but this is my March Madness gospel—bracket’s clean, let’s see who survives! Let’s freaking go, degenerates!
-
 @ 7d33ba57:1b82db35
2025-03-24 15:40:17
@ 7d33ba57:1b82db35
2025-03-24 15:40:17Located in the Cabo de Gata-Níjar Natural Park, Agua Amarga is a small, picturesque fishing village on the southeastern coast of Spain. Known for its crystal-clear waters, whitewashed houses, and peaceful atmosphere, this is the perfect spot for a relaxing Mediterranean escape.
🏖️ Top Things to See & Do in Agua Amarga
1️⃣ Playa de Agua Amarga 🏝️
- A beautiful, sandy beach with shallow, turquoise waters.
- Family-friendly with beach bars (chiringuitos) and restaurants nearby.
- Great for swimming, paddleboarding, and sunbathing.
2️⃣ Cala de Enmedio – A Hidden Paradise 🌊
- A secluded cove with soft sand and smooth rock formations.
- Reachable by a 30-minute hike or by kayak.
- One of the most photogenic beaches in Cabo de Gata!
3️⃣ Cala del Plomo 🏞️
- Another pristine, unspoiled cove surrounded by dramatic cliffs.
- Accessible by a short hike or 4x4 vehicle.
- A perfect spot for snorkeling and enjoying nature in peace.
4️⃣ Boat & Kayak Excursions 🚤
- Explore the rugged coastline, caves, and hidden beaches by sea.
- Some tours include stops at Cala de San Pedro, a remote beach with an alternative hippie community.
5️⃣ Hiking & Nature Trails 🌿
- Agua Amarga is surrounded by stunning volcanic landscapes within Cabo de Gata Natural Park.
- The Sendero de la Cala de Enmedio is a scenic hike with breathtaking views.
🍽️ What to Eat in Agua Amarga
- Gambas rojas de Garrucha – Sweet red prawns 🦐
- Arroz caldoso de marisco – A rich, brothy seafood rice dish 🍚🐟
- Pulpo a la brasa – Grilled octopus, a local delicacy 🐙
- Pescado fresco – Fresh fish straight from the sea 🐠
- Tarta de almendra – A delicious almond cake for dessert 🍰
🚗 How to Get to Agua Amarga
🚘 By Car: ~1 hour from Almería via A-7 & AL-5106
🚌 By Bus: Limited services from Almería; renting a car is recommended for flexibility
✈️ By Air: Nearest airport is Almería Airport (LEI), about 50 km away💡 Tips for Visiting Agua Amarga
✅ Best time to visit? Spring & early autumn – warm but not too crowded 🌞
✅ Bring water & snacks if visiting remote beaches – no facilities in hidden coves 🏝️
✅ Rent a kayak or boat for the best way to explore the coastline 🚣♂️
✅ Stay overnight to enjoy the peaceful ambiance after the day-trippers leave 🌅 -
 @ 94a6a78a:0ddf320e
2025-02-19 21:10:15
@ 94a6a78a:0ddf320e
2025-02-19 21:10:15Nostr is a revolutionary protocol that enables decentralized, censorship-resistant communication. Unlike traditional social networks controlled by corporations, Nostr operates without central servers or gatekeepers. This openness makes it incredibly powerful—but also means its success depends entirely on users, developers, and relay operators.
If you believe in free speech, decentralization, and an open internet, there are many ways to support and strengthen the Nostr ecosystem. Whether you're a casual user, a developer, or someone looking to contribute financially, every effort helps build a more robust network.
Here’s how you can get involved and make a difference.
1️⃣ Use Nostr Daily
The simplest and most effective way to contribute to Nostr is by using it regularly. The more active users, the stronger and more valuable the network becomes.
✅ Post, comment, and zap (send micro-payments via Bitcoin’s Lightning Network) to keep conversations flowing.\ ✅ Engage with new users and help them understand how Nostr works.\ ✅ Try different Nostr clients like Damus, Amethyst, Snort, or Primal and provide feedback to improve the experience.
Your activity keeps the network alive and helps encourage more developers and relay operators to invest in the ecosystem.
2️⃣ Run Your Own Nostr Relay
Relays are the backbone of Nostr, responsible for distributing messages across the network. The more independent relays exist, the stronger and more censorship-resistant Nostr becomes.
✅ Set up your own relay to help decentralize the network further.\ ✅ Experiment with relay configurations and different performance optimizations.\ ✅ Offer public or private relay services to users looking for high-quality infrastructure.
If you're not technical, you can still support relay operators by subscribing to a paid relay or donating to open-source relay projects.
3️⃣ Support Paid Relays & Infrastructure
Free relays have helped Nostr grow, but they struggle with spam, slow speeds, and sustainability issues. Paid relays help fund better infrastructure, faster message delivery, and a more reliable experience.
✅ Subscribe to a paid relay to help keep it running.\ ✅ Use premium services like media hosting (e.g., Azzamo Blossom) to decentralize content storage.\ ✅ Donate to relay operators who invest in long-term infrastructure.
By funding Nostr’s decentralized backbone, you help ensure its longevity and reliability.
4️⃣ Zap Developers, Creators & Builders
Many people contribute to Nostr without direct financial compensation—developers who build clients, relay operators, educators, and content creators. You can support them with zaps! ⚡
✅ Find developers working on Nostr projects and send them a zap.\ ✅ Support content creators and educators who spread awareness about Nostr.\ ✅ Encourage builders by donating to open-source projects.
Micro-payments via the Lightning Network make it easy to directly support the people who make Nostr better.
5️⃣ Develop New Nostr Apps & Tools
If you're a developer, you can build on Nostr’s open protocol to create new apps, bots, or tools. Nostr is permissionless, meaning anyone can develop for it.
✅ Create new Nostr clients with unique features and user experiences.\ ✅ Build bots or automation tools that improve engagement and usability.\ ✅ Experiment with decentralized identity, authentication, and encryption to make Nostr even stronger.
With no corporate gatekeepers, your projects can help shape the future of decentralized social media.
6️⃣ Promote & Educate Others About Nostr
Adoption grows when more people understand and use Nostr. You can help by spreading awareness and creating educational content.
✅ Write blogs, guides, and tutorials explaining how to use Nostr.\ ✅ Make videos or social media posts introducing new users to the protocol.\ ✅ Host discussions, Twitter Spaces, or workshops to onboard more people.
The more people understand and trust Nostr, the stronger the ecosystem becomes.
7️⃣ Support Open-Source Nostr Projects
Many Nostr tools and clients are built by volunteers, and open-source projects thrive on community support.
✅ Contribute code to existing Nostr projects on GitHub.\ ✅ Report bugs and suggest features to improve Nostr clients.\ ✅ Donate to developers who keep Nostr free and open for everyone.
If you're not a developer, you can still help with testing, translations, and documentation to make projects more accessible.
🚀 Every Contribution Strengthens Nostr
Whether you:
✔️ Post and engage daily\ ✔️ Zap creators and developers\ ✔️ Run or support relays\ ✔️ Build new apps and tools\ ✔️ Educate and onboard new users
Every action helps make Nostr more resilient, decentralized, and unstoppable.
Nostr isn’t just another social network—it’s a movement toward a free and open internet. If you believe in digital freedom, privacy, and decentralization, now is the time to get involved.
-
 @ 5de23b9a:d83005b3
2025-02-19 03:47:19
@ 5de23b9a:d83005b3
2025-02-19 03:47:19In a digital era that is increasingly controlled by large companies, the emergence of Nostr (Notes and Other Stuff Transmitted by Relays) is a breath of fresh air for those who crave freedom of expression.
Nostr is a cryptography-based protocol that allows users to send and receive messages through a relay network. Unlike conventional social media such as Twitter or Facebook
1.Full Decentralization: No company or government can remove or restrict content.
2.Sensor-Resistant: Information remains accessible despite blocking attempts.
3.Privacy and Security: Uses cryptography to ensure that only users who have the keys can access their messages.* **
-
 @ 9e69e420:d12360c2
2025-02-17 17:12:01
@ 9e69e420:d12360c2
2025-02-17 17:12:01President Trump has intensified immigration enforcement, likening it to a wartime effort. Despite pouring resources into the U.S. Immigration and Customs Enforcement (ICE), arrest numbers are declining and falling short of goals. ICE fell from about 800 daily arrests in late January to fewer than 600 in early February.
Critics argue the administration is merely showcasing efforts with ineffectiveness, while Trump seeks billions more in funding to support his deportation agenda. Increased involvement from various federal agencies is intended to assist ICE, but many lack specific immigration training.
Challenges persist, as fewer immigrants are available for quick deportation due to a decline in illegal crossings. Local sheriffs are also pressured by rising demands to accommodate immigrants, which may strain resources further.
-
 @ 4259e401:8e20e9a6
2025-03-24 14:27:27
@ 4259e401:8e20e9a6
2025-03-24 14:27:27[MVP: Gigi! How do I lightning prism this?]
If I could send a letter to myself five years ago, this book would be it.
I’m not a Bitcoin expert. I’m not a developer, a coder, or an economist.
I don’t have credentials, connections, or capital.
I’m a blue-collar guy who stumbled into Bitcoin almost exactly four years ago, and like everyone else, I had to wrestle with it to understand it.
Bitcoin is one of the most misunderstood, misrepresented, and misinterpreted ideas of our time - not just because it’s complex, but because its very structure makes it easy to distort.
It’s decentralized and leaderless, which means there’s no single voice to clarify what it is or defend it from misinformation.
That’s a feature, not a bug, but it means that understanding Bitcoin isn’t easy.
It’s a system that doesn’t fit into any of our existing categories. It’s not a company. It’s not a product. It’s not a government.
There’s no marketing department, no headquarters, no CEO.
That makes it uniquely resistant to corruption, but also uniquely vulnerable to disinformation.
Whether through negligence or malice, Bitcoin is constantly misunderstood - by skeptics who think it’s just a Ponzi scheme, by opportunists looking to cash in on the hype, by scammers who use the name to push worthless imitations, and by critics who don’t realize they’re attacking a strawman.
If you’re new to Bitcoin, you have to fight through layers of noise before you can even see the signal.
And that process isn’t instant.
Even if you could explain digital signatures off the top of your head, even if you could hash SHA-256 by hand, even if you had a perfect technical understanding of every moving part - you still wouldn’t get it.
Bitcoin isn’t just technology. It’s a shift in incentives, a challenge to power, an enforcer of sovereignty. It resists censorship.
A simple open ledger - yet it shakes the world.
Archimedes asked for a lever and a place to stand, and he could move the world.
Satoshi gave us both.
The lever is Bitcoin - an economic system with perfect game theory, incorruptible rules, and absolute scarcity.
The place to stand is the open-source, decentralized network, where anyone can verify, participate, and build without permission.
And what comes out of this seemingly simple equation?
The entire rearchitecture of trust. The separation of money and state.
A foundation upon which artificial intelligence must negotiate with the real world instead of manipulating it.
A digital economy where energy, computation, and value flow in perfect symmetry, refining themselves in an endless virtuous cycle.
Bitcoin started as a whitepaper.
Now it’s a lifeline, an immune system, a foundation, a firewall, a torch passed through time.
From such a small set of rules - 21 million divisible units, cryptographic ownership, and a fixed issuance schedule - emerges something unstoppable.
Something vast enough to absorb and constrain the intelligence of machines, to resist the distortions of human greed, to create the rails for a world that is freer, more sovereign, more aligned with truth than anything that came before it.
It’s proof that sometimes, the most profound revolutions begin with the simplest ideas. That’s why this book exists.
Bitcoin isn’t something you learn - it’s something you unlearn first.
You start with assumptions about money, value, and authority that have been baked into you since birth. And then, piece by piece, you chip away at them.
It’s like peeling an onion – it takes time and effort.
*And yes, you might shed some tears! *
At first, you might come for the speculation. A lot of people do. But those who stay - who actually take the time to understand what’s happening - don’t stay for the profits.
They stay for the principles.
If you’re holding this book, you’re somewhere on that journey.
Maybe you’re at the very beginning, trying to separate the signal from the noise.
Maybe you’ve been down the rabbit hole for years, looking for a way to articulate what you already know deep in your bones.
Either way, this is for you.
It’s not a technical manual, and it’s not a sales pitch. It’s the book I wish I had when I started.
So if you’re where I was, consider this a message in a bottle, thrown back through time. A hand reaching through the fog, saying:
“Keep going. It’s worth it.”
Preface The End of The Beginning
March 2025.
The moment has arrived. Most haven’t even noticed, let alone processed it. The United States is setting up a Bitcoin (Bitcoin-only!) strategic reserve.
It’s not a theory. Not an idea. The order is signed, the ink is dried.
The people who have been wrong, over and over (and over!) again - for years! - fumble for explanations, flipping through the wreckage of their previous predictions:
“Bubble…’’ “Fad…” “Ponzi…”
No longer.
The same analysts who once sneered are now adjusting their forecasts to protect what’s left of their credibility. Those who dismissed it are now trapped in a slow, humiliating realization: Bitcoin does not require their approval.
It never did.
Something fundamental has shifted, and the air is thick with a paradoxical cocktail of triumph and panic. Bitcoiners saw this coming. Not because they had insider information, but because they understood first principles when everyone else was still playing pretend.
Bitcoin was never just surviving.
It was infiltrating.
The question is no longer whether Bitcoin will succeed.
It already has.
The only question that remains is who understands, and who is still in denial.
Think back to 2022.
At its peak, FTX was one of the world’s largest cryptocurrency exchanges, valued at $32 billion and backed by blue-chip investors. It promised a sophisticated, institutional-grade trading platform, attracting retail traders, hedge funds, and politicians alike. Sam Bankman-Fried, with his disheveled hair and cargo shorts, was its eccentric figurehead, a billionaire who slept on a bean bag and spoke of philanthropy.
Then the illusion shattered.
FTX collapsed overnight, an implosion so violent it left an entire industry scrambling for cover. One moment, Sam Bankman-Fried was the golden boy of crypto - genius quant, regulatory darling, effective altruist™.
The next, he was just another fraudster in handcuffs.
Billions vanished. Customers locked out. Hedge funds liquidated.
Politicians who had once taken photos with SBF and smiled at his political donations, suddenly pretended they had no idea who he was. The same regulators who were supposed to prevent disasters like this stood slack-jawed, acting as if they hadn’t been having closed-door meetings with FTX months before the collapse.
But FTX wasn’t just a scandal, it was a filter.
If you were Bitcoin-only, with your satoshis in cold storage, you didn’t even flinch. From your perspective, nothing important changed:
A new Bitcoin block still arrived every ten minutes (on average). The supply cap of 21 million bitcoins remained untouched. Ownership was still protected by public/private key cryptography.
You were literally unaffected.
You had already updated your priors:
“If you don’t hold your own keys, you own nothing.” “Bitcoin is not ‘crypto’.” “’Crypto’ is a casino.”
FTX was just another financial fire, another chapter in the never-ending saga of people trusting systems that had already proven themselves untrustworthy.
That moment was a prelude.
The U.S. Bitcoin pivot is the paradigm shift.
The Eukaryotic Revolution Is Upon Us
In biology, abiogenesis is when life emerged from non-life - a fragile, uncertain process where the first microscopic self-replicators struggled to survive against hostile conditions. That was Bitcoin’s early history. It had to fight for its existence, attacked by governments, dismissed by economists, ridiculed by mainstream media.
But it survived.
That era is over. We have entered the Eukaryotic Revolution.
This is the moment in evolutionary history when simple lifeforms evolved into something structurally complex - organisms with nuclei, internal scaffolding, and the ability to form multicellular cooperatives and populate diverse ecosystems. Once this transformation happened, there was no going back. Bitcoin is going through its own Eukaryotic leap.
Once an outsider, dismissed and ridiculed, it is maturing into an integrated, resilient force within the global financial system.
On March 2, 2025, the Trump administration announced a Crypto Strategic Reserve.
At first, it wasn’t just Bitcoin - it included XRP, SOL, and ADA, a desperate attempt to appease the altcoin industry. A political move, not an economic one.
For about five minutes, the broader crypto industry cheered. Then came the pushback.
Bitcoiners called it immediately: mixing Bitcoin with centralized altcoin grifts was like adding lead weights to a life raft.
Institutional players rejected it outright: sovereign reserves need hard assets, not tech company tokens. The government realized, almost immediately, that it had made a mistake.
By March 6, 2025, the pivot was complete.
Strategic Bitcoin reserve confirmed. The President signed an executive order, and legislation has been introduced in the United States House of Representatives.
The U.S. government’s official bitcoin policy: hold, don’t sell. Look for ways to acquire more.
Altcoins relegated to second-tier status, treated as fundamentally separate from and inferior to bitcoin. The government’s official policy: sell, and do not actively accumulate more (ouch!).
“Bitcoin maximalism” – the belief that any cryptocurrency other than bitcoin lies on a spectrum between “bad idea” and outright scam - wasn’t vindicated by debate.
It was vindicated by economic reality.
When the government was forced to choose what belonged in a sovereign reserve, it wasn’t even close. Bitcoin stood alone.
“There is no second best.” -Michael Saylor
Who This Book Is For: The Three Types of Readers
You’re here for a reason.
Maybe you felt something shift.
Maybe you saw the headlines, sensed the undercurrents, or simply couldn’t ignore the growing drumbeat any longer.
Maybe you’ve been here all along, waiting for the world to catch up.
Whatever brought you to this book, one thing is certain: you’re curious enough to learn more.
Bitcoin forces a reevaluation of assumptions - about money, trust, power, and the very foundations of the economic order. How much of that process you’ve already undergone will determine how you read these pages.
1. The Layperson → new, curious, maybe skeptical. Bitcoin probably looks like chaos to you right now. One person says it’s the future. Another says it’s a scam. The price crashes. The price doubles. The news is either breathless excitement or total doom. How the hell are you supposed to figure this out?
If that’s you, welcome.
This book was built for you.
You don’t need to be an economist, a technologist, or a finance geek to understand what’s in these pages. You just need an open mind and the willingness to engage with new ideas - ideas that will, if you follow them far enough, challenge some of your deepest assumptions.
Bitcoin is not an investment. Bitcoin is not a company. Bitcoin is not a stock, a trend, or a passing phase.
Bitcoin is a paradigm shift. And by the time you reach the last page, you won’t need to be convinced of its importance. You’ll see it for yourself.
2. The Student → understand the basics, want to go deeper.
You’ve already stepped through the door.
You’ve realized Bitcoin is more than just digital gold. You understand decentralization, scarcity, censorship resistance… But the deeper you go, the more you realize just how much there is to understand.
3. The Expert → You’ve been in the game for years.
You’ve put in the time.
You don’t need another book telling you Bitcoin will succeed. You already know.
You’re here because you want sharper tools.
Tighter arguments.
A way to shut down nonsense with fewer words, and more force.
Maybe this book will give you a new way to frame an idea you’ve been struggling to convey.
Maybe it will help you refine your messaging and obliterate some lingering doubts in the minds of those around you.
Or maybe this will simply be the book you hand to the next person who asks, “Okay… but what’s the deal with Bitcoin?” so you don’t have to keep explaining it from scratch.
*If you’re already deep in the weeds, you can probably skip Part I (Foundations) without missing much - unless you’re curious about a particular way of putting a particular thing. *
Part II (Resilience) is where things get more interesting. Why you want to run a node, even if you don’t know it yet. The energy debate, stripped of media hysteria. The legend of Satoshi, and what actually matters about it.
If you’re a hardcore cypherpunk who already speaks in block heights and sending Zaps on NOSTR, feel free to jump straight to Part III (The Peaceful Revolution). Chapter 15, “The Separation of Money and State” is where the gloves come off.
Bitcoin isn’t just a technology. Bitcoin isn’t just an economic movement. Bitcoin is a lens.
And once you start looking through it, the world never looks the same again.
This book will teach you what Bitcoin is, as much as it will help you understand why Bitcoiners think the way they do.
It isn’t just something you learn about.
Especially not in one sitting, or from one book.
It’s something you grow to realize.
Regardless of which category you fall into, you’ve already passed the first test.
You’re still reading.
You haven’t dismissed this outright. You haven’t scoffed, rolled your eyes, or walked away. You’re at least curious.
And that’s all it takes.
Curiosity is the only filter that matters.
The rest takes care of itself.
The Essential Role of Memes Memes won the narrative war - it wasn’t textbooks, research papers, or whitepapers that did it. Bitcoin spread the same way evolution spreads successful genes - through replication, variation, and selection. Richard Dawkins coined the term “meme” in The Selfish Gene, describing it as a unit of cultural transmission - behaving much like a gene. Memes replicate, mutate, and spread through culture. Just as natural selection filters out weak genes, memetic selection filters out weak ideas.
But Bitcoin memes weren’t just jokes.
They were premonitions.
The most powerful ideas are often compact, inarguable, and contagious - and Bitcoin’s memes were all three. They cut through complexity like a scalpel, distilling truths into phrases so simple, so undeniable, that they burrowed into the mind and refused to leave.
"Bitcoin fixes this." "Not Your Keys, Not Your Coins." "Number Go Up."
Each of these is more than just a slogan.
They’re memetic payloads, compressed packets of truth that can carry everything you need to understand about Bitcoin in just a few words.
They spread through conversations, through tweets, through shitposts, through relentless repetition.
They bypassed the gatekeepers of financial knowledge, infecting minds before Wall Street even understood what was happening.
And they didn’t just spread.
They reshaped language itself.
Before Bitcoin, the word fiat was a sterile economic term, borrowed from Latin, meaning "by decree." It had no weight, no controversy - just a neutral descriptor for government-issued money.
But Bitcoiners forced a memetic shift.
They didn’t just make fiat mainstream.
**They made it radioactive. **
They stripped away the academic detachment and revealed its true essence:
money because I said so.
No backing. No inherent value.
Just a command.
And of course, an unspoken threat -
"Oh, and by the way, I have a monopoly on violence, so you’d better get on board."
This wasn’t just linguistic evolution; it was a memetic coup.
Bitcoiners took a sterile term and injected it with an unavoidable truth: fiat money exists not because it is chosen, but because it is imposed.
Central banks, governments, and financial institutions now use the term fiat without a second thought.
The meme has done its work.
A word that was once neutral, now carries an implicit critique - a quiet but persistent reminder that there is an alternative.
Bitcoin didn’t just challenge the financial system - it rewired the language we use to describe it.
“Money printer go BRRRRRR" did more damage to the Fed’s reputation than a thousand Austrian economics treatises ever could.
Memes exposed what balance sheets and policy reports tried to obscure. They turned abstract economic forces into something visceral, something undeniable.
And now - they are historical markers of the shift, the fossil record of our collective consciousness coming to terms with something fundamentally new in the universe.
The old world relied on authority, institutional credibility, and narrative control.
Bitcoin broke through with memes, first principles, and lived experience.
This wasn’t just an ideological battle.
It was an evolutionary process.
The weaker ideas died. The strongest ones survived.
Once a meme - in other words, an idea - takes hold, there is nothing - no law, no regulation, no institution, no government - that can stop it.
Bitcoin exists. It simply is.
And it will keep producing blocks, every ten minutes, whether you get it or not.
This book isn’t a trading manual.
It won’t teach you how to time the market, maximize your gains, or set up a wallet.
It’s a carefully curated collection of memes, giving you the prerequisite mental scaffolding to grok the greatest monetary shift in human history.
A shift that has already begun.
The only thing to decide is whether you’re watching from the sidelines or whether you’re part of it.
The rest is up to you.
How This Book Is Structured Bitcoin spreads like an evolutionary force - through memes. Each chapter in this book isn’t just an idea, it’s a memetic payload, designed to install the concepts that make Bitcoin inevitable. The book is broken into three phases:
*I. Foundations *** Memes as Mental Antivirus The first layer cuts through noise and filters out distractions. "Bitcoin Only" is the first test - if you get this one wrong, you waste years chasing ghosts. "Don’t Trust, Verify" rewires how you think about truth. And "Not Your Keys, Not Your Coins"? If you learn it the hard way, it’s already too late.
II. Resilience Memes as Weapons in the Information War Here’s where Bitcoin earns its survival. "Shitcoiners Get REKT" is a law, not an opinion. "Fork Around and Find Out" proves that you don’t change Bitcoin - Bitcoin changes you. "Antifragile, Unstoppable" shows how every attack on Bitcoin has only made it stronger.
III. The Peaceful Revolution ** Memes as Reality Distortion Fields By now, Bitcoin isn’t just an asset - it’s a lens. "Separation of Money and State" isn’t a theory; it’s happening in real time. "Fix the Money, Fix the World" isn’t a slogan; it’s a diagnosis. And "Tick Tock, Next Block"? No matter what happens, Bitcoin keeps producing blocks.
These aren’t just memes. They’re scaffolding for a new way of thinking. Each one embeds deeper until you stop asking if Bitcoin will succeed - because you realize it already has.
Next: Chapter 1: Bitcoin Only. ** For now, it’s a heuristic - an efficient filter that separates signal from noise, with minimal effort.
But by the time you finish this book, it won’t be a heuristic anymore.
It will be something you know.Welcome to the rabbit hole.
-
 @ 42342239:1d80db24
2025-02-16 08:39:59
@ 42342239:1d80db24
2025-02-16 08:39:59Almost 150 years ago, the British newspaper editor William Thomas Stead wrote that "the editorial pen is a sceptre of power, compared with which the sceptre of many a monarch is but a gilded lath". He had begun to regard journalism as something more than just conveying information - the journalist or editor could become a ruler.
Times had certainly changed compared to a few hundred years earlier. Before Gutenberg's invention of the printing press, it was mainly the church that controlled the dissemination of information in Europe, but when Stead put pen to paper, this control had shifted to newspapers, schools, and universities. Eventually, technologies like radio and TV entered the scene, but the power dynamics remained asymmetrical - only a few could send information to the many.
However, with the emergence of the internet, and especially with the spread of social media, a significant change followed. Instead of only a few being able to send information to the many, many could send to many. Almost anyone could now create their own newspaper, radio, or TV channel. The power over information dissemination was decentralised.
Ten years ago, Roberta Alenius, who was then press secretary for Sweden's Prime Minister Fredrik Reinfeldt of the Moderate Party, shared her experiences with Social Democratic and Moderate Party internet activists on social media. She reported that social media played a significant role in how news "comes out" and is shaped, and that journalism was now downstream of social media. Five years later, NATO's then-Secretary-General Jens Stoltenberg said that "NATO must be prepared for both conventional and hybrid threats: from tanks to tweets." This finally underscores the importance of social media.
Elon Musk, who took over X (formerly Twitter) in 2022, has claimed that "it's absolutely fundamental and transformative that the people actually get to decide the news and narrative and what's important," and that citizen journalism is the future.
While his platform allows most expressions - for better or worse - the reach of messages is instead limited ("freedom of speech does not mean freedom of reach "). X has also opened its recommendation algorithm to the outside world by making it open-source. Although this is a welcome step, the fact remains that it's impossible to know which code is actually used and what adjustments are made by humans or algorithms.
William Thomas Stead's "sceptre of power", which has wandered from the church to newspaper and TV editorial offices, and now to citizens according to Elon Musk, risks being transferred to algorithms' opaque methods?
Instead of talking about "toxic algorithms" and TikTok bans, like the so many do today, we should ask ourselves more fundamental questions. What happens when algorithms are no longer objective (how can they ever be?), but instead become tools for shaping our reality? Perhaps our greatest challenge today is not deciding who should govern the information landscape, but instead recognising that no one is up to the task - not even well-ventilated computers.
-
 @ fd208ee8:0fd927c1
2025-02-15 07:02:08
@ fd208ee8:0fd927c1
2025-02-15 07:02:08E-cash are coupons or tokens for Bitcoin, or Bitcoin debt notes that the mint issues. The e-cash states, essentially, "IoU 2900 sats".
They're redeemable for Bitcoin on Lightning (hard money), and therefore can be used as cash (softer money), so long as the mint has a good reputation. That means that they're less fungible than Lightning because the e-cash from one mint can be more or less valuable than the e-cash from another. If a mint is buggy, offline, or disappears, then the e-cash is unreedemable.
It also means that e-cash is more anonymous than Lightning, and that the sender and receiver's wallets don't need to be online, to transact. Nutzaps now add the possibility of parking transactions one level farther out, on a relay. The same relays that cannot keep npub profiles and follow lists consistent will now do monetary transactions.
What we then have is * a transaction on a relay that triggers * a transaction on a mint that triggers * a transaction on Lightning that triggers * a transaction on Bitcoin.
Which means that every relay that stores the nuts is part of a wildcat banking system. Which is fine, but relay operators should consider whether they wish to carry the associated risks and liabilities. They should also be aware that they should implement the appropriate features in their relay, such as expiration tags (nuts rot after 2 weeks), and to make sure that only expired nuts are deleted.
There will be plenty of specialized relays for this, so don't feel pressured to join in, and research the topic carefully, for yourself.
https://github.com/nostr-protocol/nips/blob/master/60.md
-
 @ 0fa80bd3:ea7325de
2025-02-14 23:24:37
@ 0fa80bd3:ea7325de
2025-02-14 23:24:37intro
The Russian state made me a Bitcoiner. In 1991, it devalued my grandmother's hard-earned savings. She worked tirelessly in the kitchen of a dining car on the Moscow–Warsaw route. Everything she had saved for my sister and me to attend university vanished overnight. This story is similar to what many experienced, including Wences Casares. The pain and injustice of that time became my first lessons about the fragility of systems and the value of genuine, incorruptible assets, forever changing my perception of money and my trust in government promises.
In 2014, I was living in Moscow, running a trading business, and frequently traveling to China. One day, I learned about the Cypriot banking crisis and the possibility of moving money through some strange thing called Bitcoin. At the time, I didn’t give it much thought. Returning to the idea six months later, as a business-oriented geek, I eagerly began studying the topic and soon dove into it seriously.
I spent half a year reading articles on a local online journal, BitNovosti, actively participating in discussions, and eventually joined the editorial team as a translator. That’s how I learned about whitepapers, decentralization, mining, cryptographic keys, and colored coins. About Satoshi Nakamoto, Silk Road, Mt. Gox, and BitcoinTalk. Over time, I befriended the journal’s owner and, leveraging my management experience, later became an editor. I was drawn to the crypto-anarchist stance and commitment to decentralization principles. We wrote about the economic, historical, and social preconditions for Bitcoin’s emergence, and it was during this time that I fully embraced the idea.
It got to the point where I sold my apartment and, during the market's downturn, bought 50 bitcoins, just after the peak price of $1,200 per coin. That marked the beginning of my first crypto winter. As an editor, I organized workflows, managed translators, developed a YouTube channel, and attended conferences in Russia and Ukraine. That’s how I learned about Wences Casares and even wrote a piece about him. I also met Mikhail Chobanyan (Ukrainian exchange Kuna), Alexander Ivanov (Waves project), Konstantin Lomashuk (Lido project), and, of course, Vitalik Buterin. It was a time of complete immersion, 24/7, and boundless hope.
After moving to the United States, I expected the industry to grow rapidly, attended events, but the introduction of BitLicense froze the industry for eight years. By 2017, it became clear that the industry was shifting toward gambling and creating tokens for the sake of tokens. I dismissed this idea as unsustainable. Then came a new crypto spring with the hype around beautiful NFTs – CryptoPunks and apes.
I made another attempt – we worked on a series called Digital Nomad Country Club, aimed at creating a global project. The proceeds from selling images were intended to fund the development of business tools for people worldwide. However, internal disagreements within the team prevented us from completing the project.
With Trump’s arrival in 2025, hope was reignited. I decided that it was time to create a project that society desperately needed. As someone passionate about history, I understood that destroying what exists was not the solution, but leaving everything as it was also felt unacceptable. You can’t destroy the system, as the fiery crypto-anarchist voices claimed.
With an analytical mindset (IQ 130) and a deep understanding of the freest societies, I realized what was missing—not only in Russia or the United States but globally—a Bitcoin-native system for tracking debts and financial interactions. This could return control of money to ordinary people and create horizontal connections parallel to state systems. My goal was to create, if not a Bitcoin killer app, then at least to lay its foundation.
At the inauguration event in New York, I rediscovered the Nostr project. I realized it was not only technologically simple and already quite popular but also perfectly aligned with my vision. For the past month and a half, using insights and experience gained since 2014, I’ve been working full-time on this project.
-
 @ c5128106:9b820f34
2025-03-24 13:50:16
@ c5128106:9b820f34
2025-03-24 13:50:16Continue to dishonour yourself, my soul ! Neither will you have much time left to do yourself honour. For the life of each man is almost up already ; and yet, instead of paying a due regard to yourself, you place your happiness in the souls of other men.
-
 @ e3ba5e1a:5e433365
2025-02-13 06:16:49
@ e3ba5e1a:5e433365
2025-02-13 06:16:49My favorite line in any Marvel movie ever is in “Captain America.” After Captain America launches seemingly a hopeless assault on Red Skull’s base and is captured, we get this line:
“Arrogance may not be a uniquely American trait, but I must say, you do it better than anyone.”
Yesterday, I came across a comment on the song Devil Went Down to Georgia that had a very similar feel to it:

America has seemingly always been arrogant, in a uniquely American way. Manifest Destiny, for instance. The rest of the world is aware of this arrogance, and mocks Americans for it. A central point in modern US politics is the deriding of racist, nationalist, supremacist Americans.
That’s not what I see. I see American Arrogance as not only a beautiful statement about what it means to be American. I see it as an ode to the greatness of humanity in its purest form.
For most countries, saying “our nation is the greatest” is, in fact, twinged with some level of racism. I still don’t have a problem with it. Every group of people should be allowed to feel pride in their accomplishments. The destruction of the human spirit since the end of World War 2, where greatness has become a sin and weakness a virtue, has crushed the ability of people worldwide to strive for excellence.
But I digress. The fears of racism and nationalism at least have a grain of truth when applied to other nations on the planet. But not to America.
That’s because the definition of America, and the prototype of an American, has nothing to do with race. The definition of Americanism is freedom. The founding of America is based purely on liberty. On the God-given rights of every person to live life the way they see fit.
American Arrogance is not a statement of racial superiority. It’s barely a statement of national superiority (though it absolutely is). To me, when an American comments on the greatness of America, it’s a statement about freedom. Freedom will always unlock the greatness inherent in any group of people. Americans are definitionally better than everyone else, because Americans are freer than everyone else. (Or, at least, that’s how it should be.)
In Devil Went Down to Georgia, Johnny is approached by the devil himself. He is challenged to a ridiculously lopsided bet: a golden fiddle versus his immortal soul. He acknowledges the sin in accepting such a proposal. And yet he says, “God, I know you told me not to do this. But I can’t stand the affront to my honor. I am the greatest. The devil has nothing on me. So God, I’m gonna sin, but I’m also gonna win.”
Libertas magnitudo est
-
 @ a7bbc310:fe7b7be3
2025-03-24 13:18:49
@ a7bbc310:fe7b7be3
2025-03-24 13:18:49I’ve been back from Morocco for just over a month and I’ve had some time to reflect. I started writing a day by day of what I did in my trip to Morocco but that was turning out a bit boring. I couldn’t do the trip justice. I thought I’d share some of my observations instead. I’d start by saying I was only there for 5 1/2 days. 5 days in Marrakesh and half day in Essaouira
You can feel the rich culture and history Morocco has such a rich culture and history. Influence of Romans, French, Arab, Berbers, Saharan and Nomadic tribes. You can see it in the architecture, taste it in the food and hear it in the language. The streets of Marrakesh had the smells of spices, perfumes and petrol. There is a synchronised dance between everyone that occupy the streets. People, motorbikes, donkeys, carts, all jostling for position but never seeming to collide into on another.
One thing that didn’t surprise me was the high level of craftsmanship and intricate designs on some of the buildings. I was told by a tour guide that some of the calligraphy could only be understood and read by the person who wrote it.
There seemed to be a sense of community, people stopping in the street to greet each other and say hello. What surprised me about this in Marrakesh most was that it happened in such a busy city. From my experience big cities are places that you go to get lost, ignored and don’t want to be found. Scene at the end of the movie Collateral comes to mind. You know the one where he’s riding on the subway alone after being shot.
A vendor tried to sell me a pendant, a symbol of the Berber tribe that meant ‘free man’. The symbol looks similar to the one for Sats 丰. I declined to purchase since I wasn’t educated enough on the Berbers to rep a symbol.
Couldn’t get over how much stuff there was for sale! And duplications of everything, rugs, shoes , handbags, jackets. Cold mornings and evenings, warm during the day. Everyone dressed like it was winter, even when it for warmer in the afternoon. It was a special trip. I’d definitely go back. Both to visit Marrakesh and other places.
-
 @ 31da2214:af2508e2
2025-02-10 10:08:06
@ 31da2214:af2508e2
2025-02-10 10:08:06A global privacy nightmare is unfolding. The UK government secretly ordered Apple to backdoor encrypted iCloud storage worldwide—but Apple is legally forbidden from revealing this order, or they face criminal charges. This affects 2 BILLION USERS.
Here’s the full story & why it’s part of a much bigger power grab. 🧵👇 [Thread by @sayerjigmi on Thread Reader App]
1) The UK's Secret Order to Backdoor Encryption 🔓
Under the UK’s Investigatory Powers Act (IPA) 2016, Apple was served a Technical Capability Notice (TCN)—forcing them to create a backdoor for encrypted iCloud data.
This is not limited to UK users. It applies worldwide, meaning your private files are at risk, no matter where you live.
🔗 @macworld report
2) Apple’s Legal Gag Order 🤐
Apple is legally forbidden from revealing this order. If Apple even acknowledges that the UK issued this demand, they could face criminal charges.
This is a secret government order with global consequences.
3) A Global Threat to Encryption 🌍
This isn’t just about the UK (although they are leading the charge in threatening citizens in OTHER countries for violating BRITISH censorship laws!).
If Apple complies, every government in the world will demand the same access—from the US to China to authoritarian regimes.
End-to-end encryption would be effectively dead.
4) Apple’s Dilemma: Comply or Withdraw? 🚪
Apple has two choices:
- Comply & weaken encryption globally.
- Refuse & withdraw services from the UK.WhatsApp & Signal faced similar threats last year and vowed to leave the UK rather than compromise security. Will Apple do the same?
🚨 Watch the heated discussion between Damian Collins, director of CCDH (architect of the UK Online Safety Bill), and Signal’s CEO: YouTube Link
5) Why This Matters: Encryption Protects Everything 🔐
- Encryption protects financial data, health records, personal security (e.g., where you live or work), and private conversations.
- Governments always say they need backdoors for national security—but history shows they’re used for mass surveillance.
- Once a backdoor exists, hackers, rogue employees, and other governments WILL find it.
6) The UK’s War on Encryption 🛡️
The UK is trying to dominate the global surveillance & censorship landscape.
While the US, Canada, Australia, and New Zealand have supported strong encryption to mitigate cyber threats, the UK stands alone in its war on encryption.
7) The Free Speech Crackdown 🗣️
This isn’t just about encryption—it’s about control. Governments worldwide are criminalizing dissent and censoring free speech, using tech companies as their enforcement arms.
🔗 GreenMedInfo Report
8) The Global Censorship Agenda 🌐
This ties into the UK’s broader, GLOBALLY ORCHESTRATED censorship agenda:
- The Online Safety Bill criminalizes encrypted messaging & forces platforms to scan private messages.
- The Digital Services Act (EU) gives governments the power to shut down online content they don’t like.
- Leaked US-UK documents show direct coordination between UK intelligence & the Biden administration to censor online speech.
9) The Architects of Speech Policing: CCDH 🕵️♂️
The Center for Countering Digital Hate (CCDH)—a UK intelligence-backed group—has been a driving force behind global censorship.
They were caught:
- Running “black ops” to suppress RFK Jr.’s presidential campaign.
- Leading the "Kill Musk’s Twitter" directive, trying to shut down free speech on X.
- Labeling 12 private US citizens as the “Disinformation Dozen” to justify mass censorship.
🔗 Reclaim the Net Investigation
10) The Pattern is Clear: Surveillance + Censorship 🔍
1️⃣ Governments create "safety" laws to justify surveillance.
2️⃣ They pressure tech companies to enforce censorship.
3️⃣ Once encrypted services are gone, nothing is private anymore.This is the biggest attack on digital freedom in history.
11) What Can We Do? 💪
- Support companies that refuse to build backdoors (Signal, ProtonMail, etc.).
- Push for legislation that protects encryption & free speech.
- Stay informed & spread awareness—governments count on secrecy to push these policies through.
- Follow and support privacy and internet freedom organizations such as:
- @G_W_Forum
- @FFO_Freedom
- @ReclaimTheNetHQ
12) The Ultimate Power Grab: Controlling All Digital Communication 📱
If Apple caves, every other platform will be forced to follow.
📌 The UK’s Global Playbook:
- A backdoor to encryption (Investigatory Powers Act).
- A government-linked censorship network (CCDH).
- A speech-policing framework that extends worldwide (Online Safety Bill).This is a global effort to control what people can say, share, and store privately.
13) The Final Stand: Will You Comply or Resist? ⚔️🚨
They want total control—your speech, your privacy, your elections. This is the defining battle of our time.
🇬🇧 UK’s war on encryption = Global censorship blueprint.
🗳️ Election meddling + speech policing = A hijacked democracy.📢 Digital freedom is human freedom.
Stand up. Speak out. Fight back. 🏴☠️🔥
Full thread preserved by Thread Reader App.
-
 @ daa41bed:88f54153
2025-02-09 16:50:04
@ daa41bed:88f54153
2025-02-09 16:50:04There has been a good bit of discussion on Nostr over the past few days about the merits of zaps as a method of engaging with notes, so after writing a rather lengthy article on the pros of a strategic Bitcoin reserve, I wanted to take some time to chime in on the much more fun topic of digital engagement.
Let's begin by defining a couple of things:
Nostr is a decentralized, censorship-resistance protocol whose current biggest use case is social media (think Twitter/X). Instead of relying on company servers, it relies on relays that anyone can spin up and own their own content. Its use cases are much bigger, though, and this article is hosted on my own relay, using my own Nostr relay as an example.
Zap is a tip or donation denominated in sats (small units of Bitcoin) sent from one user to another. This is generally done directly over the Lightning Network but is increasingly using Cashu tokens. For the sake of this discussion, how you transmit/receive zaps will be irrelevant, so don't worry if you don't know what Lightning or Cashu are.
If we look at how users engage with posts and follows/followers on platforms like Twitter, Facebook, etc., it becomes evident that traditional social media thrives on engagement farming. The more outrageous a post, the more likely it will get a reaction. We see a version of this on more visual social platforms like YouTube and TikTok that use carefully crafted thumbnail images to grab the user's attention to click the video. If you'd like to dive deep into the psychology and science behind social media engagement, let me know, and I'd be happy to follow up with another article.
In this user engagement model, a user is given the option to comment or like the original post, or share it among their followers to increase its signal. They receive no value from engaging with the content aside from the dopamine hit of the original experience or having their comment liked back by whatever influencer they provide value to. Ad revenue flows to the content creator. Clout flows to the content creator. Sales revenue from merch and content placement flows to the content creator. We call this a linear economy -- the idea that resources get created, used up, then thrown away. Users create content and farm as much engagement as possible, then the content is forgotten within a few hours as they move on to the next piece of content to be farmed.
What if there were a simple way to give value back to those who engage with your content? By implementing some value-for-value model -- a circular economy. Enter zaps.

Unlike traditional social media platforms, Nostr does not actively use algorithms to determine what content is popular, nor does it push content created for active user engagement to the top of a user's timeline. Yes, there are "trending" and "most zapped" timelines that users can choose to use as their default, but these use relatively straightforward engagement metrics to rank posts for these timelines.
That is not to say that we may not see clients actively seeking to refine timeline algorithms for specific metrics. Still, the beauty of having an open protocol with media that is controlled solely by its users is that users who begin to see their timeline gamed towards specific algorithms can choose to move to another client, and for those who are more tech-savvy, they can opt to run their own relays or create their own clients with personalized algorithms and web of trust scoring systems.
Zaps enable the means to create a new type of social media economy in which creators can earn for creating content and users can earn by actively engaging with it. Like and reposting content is relatively frictionless and costs nothing but a simple button tap. Zaps provide active engagement because they signal to your followers and those of the content creator that this post has genuine value, quite literally in the form of money—sats.

I have seen some comments on Nostr claiming that removing likes and reactions is for wealthy people who can afford to send zaps and that the majority of people in the US and around the world do not have the time or money to zap because they have better things to spend their money like feeding their families and paying their bills. While at face value, these may seem like valid arguments, they, unfortunately, represent the brainwashed, defeatist attitude that our current economic (and, by extension, social media) systems aim to instill in all of us to continue extracting value from our lives.
Imagine now, if those people dedicating their own time (time = money) to mine pity points on social media would instead spend that time with genuine value creation by posting content that is meaningful to cultural discussions. Imagine if, instead of complaining that their posts get no zaps and going on a tirade about how much of a victim they are, they would empower themselves to take control of their content and give value back to the world; where would that leave us? How much value could be created on a nascent platform such as Nostr, and how quickly could it overtake other platforms?
Other users argue about user experience and that additional friction (i.e., zaps) leads to lower engagement, as proven by decades of studies on user interaction. While the added friction may turn some users away, does that necessarily provide less value? I argue quite the opposite. You haven't made a few sats from zaps with your content? Can't afford to send some sats to a wallet for zapping? How about using the most excellent available resource and spending 10 seconds of your time to leave a comment? Likes and reactions are valueless transactions. Social media's real value derives from providing monetary compensation and actively engaging in a conversation with posts you find interesting or thought-provoking. Remember when humans thrived on conversation and discussion for entertainment instead of simply being an onlooker of someone else's life?
If you've made it this far, my only request is this: try only zapping and commenting as a method of engagement for two weeks. Sure, you may end up liking a post here and there, but be more mindful of how you interact with the world and break yourself from blind instinct. You'll thank me later.

-
 @ dc4cd086:cee77c06
2025-02-09 03:35:25
@ dc4cd086:cee77c06
2025-02-09 03:35:25Have you ever wanted to learn from lengthy educational videos but found it challenging to navigate through hours of content? Our new tool addresses this problem by transforming long-form video lectures into easily digestible, searchable content.
Key Features:
Video Processing:
- Automatically downloads YouTube videos, transcripts, and chapter information
- Splits transcripts into sections based on video chapters
Content Summarization:
- Utilizes language models to transform spoken content into clear, readable text
- Formats output in AsciiDoc for improved readability and navigation
- Highlights key terms and concepts with [[term]] notation for potential cross-referencing
Diagram Extraction:
- Analyzes video entropy to identify static diagram/slide sections
- Provides a user-friendly GUI for manual selection of relevant time ranges
- Allows users to pick representative frames from selected ranges
Going Forward:
Currently undergoing a rewrite to improve organization and functionality, but you are welcome to try the current version, though it might not work on every machine. Will support multiple open and closed language models for user choice Free and open-source, allowing for personal customization and integration with various knowledge bases. Just because we might not have it on our official Alexandria knowledge base, you are still welcome to use it on you own personal or community knowledge bases! We want to help find connections between ideas that exist across relays, allowing individuals and groups to mix and match knowledge bases between each other, allowing for any degree of openness you care.
While designed with #Alexandria users in mind, it's available for anyone to use and adapt to their own learning needs.
Screenshots
Frame Selection

This is a screenshot of the frame selection interface. You'll see a signal that represents frame entropy over time. The vertical lines indicate the start and end of a chapter. Within these chapters you can select the frames by clicking and dragging the mouse over the desired range where you think diagram is in that chapter. At the bottom is an option that tells the program to select a specific number of frames from that selection.
Diagram Extraction

This is a screenshot of the diagram extraction interface. For every selection you've made, there will be a set of frames that you can choose from. You can select and deselect as many frames as you'd like to save.
Links
- repo: https://github.com/limina1/video_article_converter
- Nostr Apps 101: https://www.youtube.com/watch?v=Flxa_jkErqE
Output
And now, we have a demonstration of the final result of this tool, with some quick cleaning up. The video we will be using this tool on is titled Nostr Apps 101 by nostr:npub1nxy4qpqnld6kmpphjykvx2lqwvxmuxluddwjamm4nc29ds3elyzsm5avr7 during Nostrasia. The following thread is an analog to the modular articles we are constructing for Alexandria, and I hope it conveys the functionality we want to create in the knowledge space. Note, this tool is the first step! You could use a different prompt that is most appropriate for the specific context of the transcript you are working with, but you can also manually clean up any discrepancies that don't portray the video accurately. You can now view the article on #Alexandria https://next-alexandria.gitcitadel.eu/publication?d=nostr-apps-101
Initially published as chained kind 1's nostr:nevent1qvzqqqqqqypzp5r5hd579v2sszvvzfel677c8dxgxm3skl773sujlsuft64c44ncqy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgwwaehxw309ahx7uewd3hkctcpzemhxue69uhhyetvv9ujumt0wd68ytnsw43z7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qgewaehxw309aex2mrp0yh8xmn0wf6zuum0vd5kzmp0qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgc7hglpn
Or view on Coracle https://coracle.social /nevent1qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgcppemhxue69uhkummn9ekx7mp0qgsdqa9md83tz5yqnrqjw07hhkpmfjpkuv9hlh5v8yhu8z274w9dv7qnnq0s3
-
 @ 078d6670:56049f0c
2025-03-24 11:28:59
@ 078d6670:56049f0c
2025-03-24 11:28:59I spent some time outside in the dark last night. After a little sleep I was wide awake again, so I ventured downstairs, rolled a joint and stepped into the darkness. No moon, no outside lights. Just stars flickering through space and landing on the sky dome, expanding my being.
There was nothing unusual. Just the usual fleeting apparitions shooting through the ether, barely visible, like they’re behind a lace curtain and I have a glimpse into the astral: light and dark winged things, miniature meteor orbs and bat shadows. This time I wasn’t listening to anything, just the inspiring tangent thoughts spiralling through my mental DNA. No cows, no lions fornicating, not even any barking dogs. (But there was a Wood Owl hooting.)
Initially, I was a little disappointed I hadn’t seen anything inexplicable, but I got over myself and expectation to always see fairies. There is a bliss in just being present (and stoned)!
When I was ready to exit the deck space, I yelled silently to myself and anyone reading my mind, “Goodnight Sky! Thank you stars for shining! Thank you planets for showing yourselves! Blessings to all the conscious beings in the Universe!”
I wasn’t prepared for what happened next. I wasn’t sure if I should run inside to get my smartphone or just watch.
An orb, a little bigger than the average star, manifested directly above my head, star-height, as far as my perception could guess. Then it disappeared after two seconds. Another one appeared in the same vicinity, and disappeared. I couldn’t tell if it was the same one reappearing in an astral (wormhole) jump, or other orbs were taking turns to greet me, because there were more, probably five in total.
How the f*!k did they hear me?
Is the sky conscious?
Does my being extend to the stars?
It felt like I was inside a lucid dream. The world was alive and acknowledging my blessings instantaneously. What impeccable manners!
I understand everything in my dream world is an extension of my consciousness. When I’m lucid I can interact with any of my dream elements and ask for meaning. There are no limits, only my imagination and unconscious beliefs.
But what is happening now?!
My reality is transforming into a dream, or the dream sandbox is becoming more real. Synchronistically, this is amazing, since my reading is taking me on a journey into western esotericism to expansive experiences through imagination to include the stars and beyond.
Soon, it’ll be time to call reality the Unreal, and the unreal Reality.
-
 @ 866e0139:6a9334e5
2025-03-24 10:54:12
@ 866e0139:6a9334e5
2025-03-24 10:54:12Vom Schrei nach dem Frieden ist hier die Luft ganz schwer,
Der Friede, der Friede, wo kommt denn der Friede her?
Der kommt nicht vom bloßen Fordern,
Der kommt nur, wenn wir ihn tun,
Und wenn in unseren Seelen die Mörderwaffen ruhn.
Wenn wir Gewalt verweigern, in Sprache, Not und Streit,
Wenn wir als Haltung lieben, Zeit unsrer Lebenszeit.
André Heller (*1947)
Die Lage ist ernst. Es ist so unübersehbar wie skandalös:
- Das "Friedensprojekt" Europäische Union rüstet zum Krieg. Orwell ist längst Realität.
- Im "Nie-Wieder-Krieg"-Land Deutschland prügeln die Kriegstreiber hunderte Milliarden durch einen abgewählten Bundestag, Wahlbetrug inklusive. Wieder mal an vorderster Front mit dabei: Kein Weltkrieg ohne uns!
- Ein Joschka Fischer, der nie gedient hat, außer an den Futtertrögen des Steuerzahlers oder von Transatlantistan, bringt die Wehrpflicht für Männer und Frauen ins Spiel. Gleichberechtigt in den Tod für die Waffenlobby!
- Der Ausnahmezustand hat nie aufgehört, bekommt nur ein neues Gesicht: die Fratze von Krieg, Tod und Leid. Corona ist abmoderiert. Das neue Virus heißt Russland, der Impfstoff „slava ukraini“, und auch bei der Finanzierung bleibt alles gleich: die Zeche zahlen (wieder mal) Sie. Diesmal doppelt. Sie dürfen zahlen und sterben, das Sonderopfer für jede Politikverwirrung zahlt in “Unserer Demokratie” immer der angebliche Souverän, der vom Nutztier jederzeit zum Schlachttier gemacht werden kann.
- Was jetzt kommt, kennen Sie schon von der Corona-Generalprobe: Spaltung, Diffamierung, Propaganda, Zensur, irre Milliardenausgaben, Ausnahmezustand, Kriegswirtschaft, Kriegszustand. Volksvertreter und Lobbyisten können sich jetzt straffrei eine goldene Nase verdienen, wenn sie ihre Wähler in die Bajonette laufen lassen. Die Strack-Zimmermanns und Kiesewetters sind die Lauterbachs und Dahmens im Tarnfleck, und sie werden bis zum letzten Wähler mutig „für das Gute“ kämpfen. Wie sich die Bilder doch gleichen:
Nicht mit uns: Erheben wir jetzt die Stimme für den Frieden!
Machen wir den Kriegstreibern einen Strich durch die Rechnung! Bringen wir die Stimmen für den Frieden an einen Tisch! Wir lassen die Friedenstaube fliegen, die erste unzensierbare Friedenspublikation der Welt auf Nostr und Pareto.
Die Vielfalt an Themen ist groß. Wir wollen aufklären und informieren:
Über Diplomatie und Strategien für den Frieden; über Lügen, Propaganda und Manipulation; über Verschwendung, Völkerrechtsbrüche und Kriegsverbrechen. Wir nehmen kein Blatt vor den Mund, egal ob hybride Kriegsführung, kognitive Kriegsführung oder sonstige neuartige Methoden der Kriegsführung. Wir wollen die Friedenswilligen vereinen und der Friedensbewegung eine starke Stimme verleihen, quer durch alle Lager. Wer auch immer jetzt das Lied vom Tod anstimmt, wird es unter den kritischen Augen der Öffentlichkeit machen müssen.
Warum wir?
- Wir haben die unzensierbare Technologie, um eine nachhaltige Publikation als Autorenblog und Newsletter aufzubauen. Diese brauchen wir auch, wir haben aus der Corona-Zensur unsere Lektion gelernt (https://pareto.space/read).
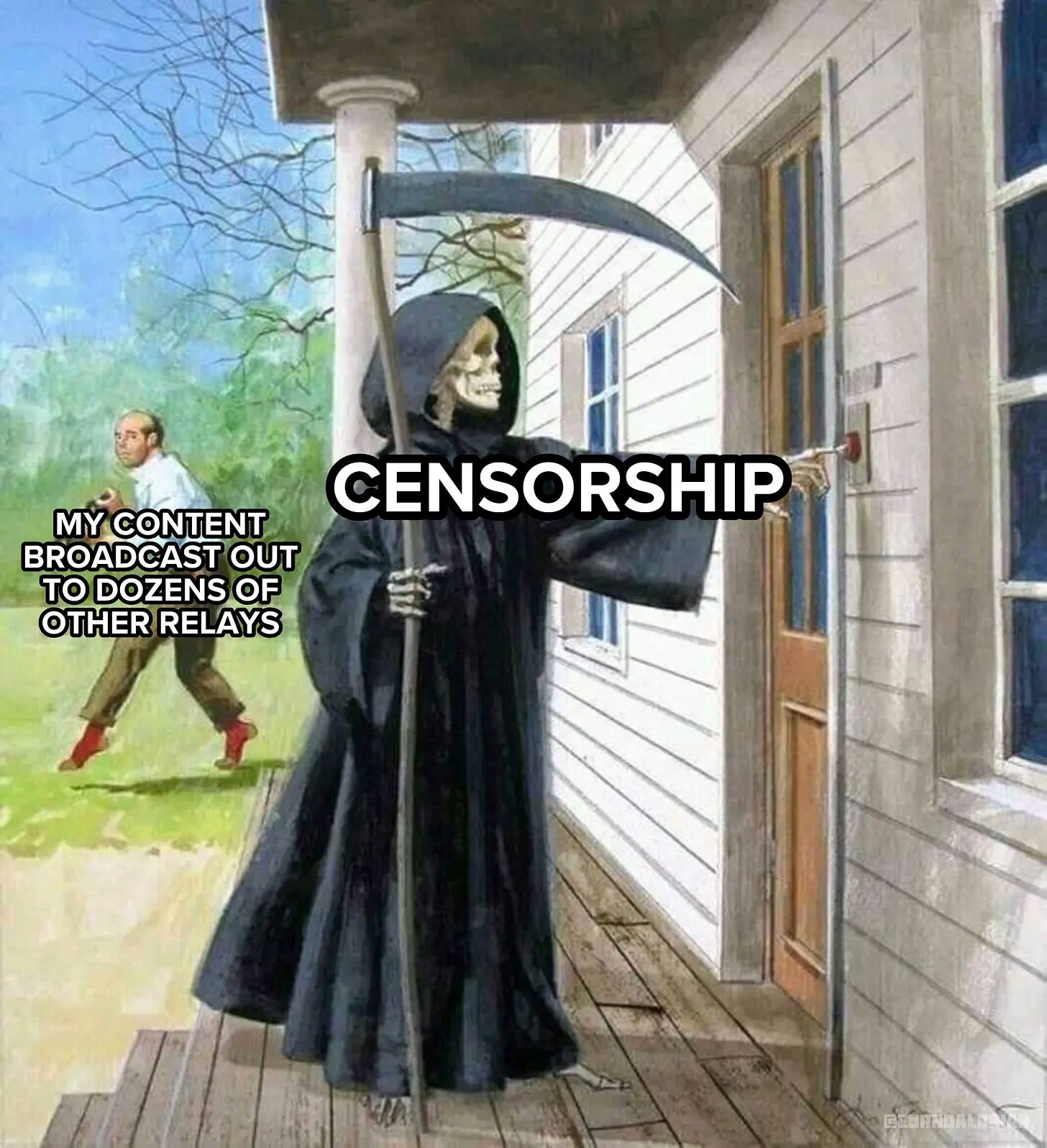
-
Wir können alle Formate bedienen, von Text, Bild und Podcast bis Video und Stream.
-
Wir werden online und in Print stattfinden (wenn Sie das wollen).
- Wir sind eine Gruppe von Autoren mit Reichweite, Erfahrung und Impact. Wir werden eine Kernredaktion haben und auf viele freie Autoren setzen, auch aus dem Ausland. Erste Kontakte sind hergestellt, das Feedback ist überwältigend.
- Wir setzen zudem von Anfang an auch auf Bürgerjournalismus und wollen jeder Stimme für den Frieden Raum und Platz bieten. Auch Sie können auf unserer freien Tribüne ("Weltbühne") publizieren und gelesen werden. Jede Stimme für den Frieden zählt!
Ich will Sie nicht mit Name dropping blenden, freue mich jedoch über bekannte erstklassige Stimmen aus der kritischen Szene, die bereits ihre Mitwirkung zugesagt haben. Diese Liste wird ständig aktualisiert (und auch ich werde Texte beitragen):
- Dr. Ulrike Guérot
- Mathias Bröckers
- Dr. Daniele Ganser
- Tom-Oliver Regenauer
- Prof. Dr. Michael Meyen
- Jonas Tögel
- Jürgen Müller
- uvm.
Sie sind Autor und wollen mit dabei sein? Schreiben Sie uns an: milosz@pareto.space
Jetzt abonnieren! Holen Sie sich die neusten Artikel der Friedenstaube in Ihr Postfach indem Sie HIER klicken.
Gründen wir eine Genossenschaft! Wir sind bereit – und Sie?
Sie entscheiden, ob und wie hoch die Friedenstaube fliegt. Wir werden eine Publikationsgenossenschaft gründen. Die Friedenstaube soll allen und niemandem gehören. Denn auch der Friede gehört allen, die ihn wollen. Krieg dagegen will immer nur eine Minderheit, am liebsten diejenigen, die nicht an die Front gehen.
Die Kriegsmaschine wird mit hunderten Milliarden geschmiert – und das ist nur der Anfang. Wir glauben, dass das Wort mächtiger ist als das Schwert. Für die Genossenschaft sammeln wir mindestens 100 000 CHF, die den Redaktionsbetrieb für ein Jahr sichern sollen. Mit einem Genossenschaftsanteil zu 1000 CHF sind Sie automatisch Verleger und bestimmen mit. Pro Person können maximal 20 Anteile gezeichnet werden, jeder Genossenschafter hat immer nur eine Stimme.
- Für 50 CHF bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):
 Für Einzahlungen in Euro:
Für Einzahlungen in Euro:Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie mich an: milosz@pareto.space oder kontakt@idw-europe.org.
Das gilt auch für Unterstützungen jenseits finanzieller Zuwendungen. Wir sind für jede Unterstützung dankbar, die hilft, das Projekt zu realisieren. Wir planen auch Printprodukte, Übersetzungen in andere Sprachen, Ausschreibungen und Wettbewerbe zum Thema Frieden uvm. Seien Sie von Anfang an mit dabei: Als Autor, Mitwirkender, Genossenschafter oder in welcher Rolle sie auch immer hilfreich zu sein glauben.
Ich kann Ihnen keine Wunder versprechen aber Sie dürfen mich an meinen bisherigen Projekten messen. Wenn ich etwas angehe, mache ich es mit voller Kraft:
Mit Ihrer Unterstützung war schon vieles möglich:
- Sie haben den “Appell für freie Debattenräume” zum sichtbarsten Zeichen gegen Cancel Culture in Europa gemacht.
- Sie haben gehofen, die Freischwebende Intelligenz zu einem der führenden Substack-Newsletter in Europa zu machen
- Sie haben “Pandamned” unterstützt, eine Corona-Doku, die mehr als 1 Mio. Menschen gesehen haben.
- Sie haben die Realisierung von Pareto unterstützt und uns geholfen, ein unzensierbares Werkzeug für Blogging/Newsletter zu bauen, weltweit einmalig.
Lassen Sie uns jetzt gemeinsam die Friedenstaube zur führenden Friedenspublikation der freien Welt aufbauen.
Lassen wir die Friedenstaube fliegen!
Jetzt.
 Herzlichen Dank, dass Sie meine Arbeit unterstützen!
Herzlichen Dank, dass Sie meine Arbeit unterstützen!Ich kann Ihnen auch manuell einen Zugang zur Publikation einrichten, wenn Sie lieber per Paypal, Überweisung oder Bitcoin (einmal Jahresbeitrag, ewiger Zugang) bezahlen. Sie erreichen mich unter kontakt@idw-europe.org
-
 @ d57360cb:4fe7d935
2025-02-06 18:31:30
@ d57360cb:4fe7d935
2025-02-06 18:31:30Mindfulness often has the misconception that by practicing you can stop your mind from thinking and obtain an empty mind.
While one can definitely achieve moments of emptiness in thinking, this view that emptiness is the goal can be the very obstacle in your way leading to frustration with the practice.
If we adjust our perspective and see mindfulness as learning to accept the situations we find ourselves in and adjust to them rather than fighting them, we achieve a kind of grace under pressure.
The thoughts are part of the practice, just like cars on the road are part of driving, or the danger of a punch is always a threat to a boxer.
The difference between the novice and the seasoned is one has accepted and acclimated to the realities of the situation instead of fighting them, in this one finds freedom.
-
 @ e3ba5e1a:5e433365
2025-02-05 17:47:16
@ e3ba5e1a:5e433365
2025-02-05 17:47:16I got into a friendly discussion on X regarding health insurance. The specific question was how to deal with health insurance companies (presumably unfairly) denying claims? My answer, as usual: get government out of it!
The US healthcare system is essentially the worst of both worlds:
- Unlike full single payer, individuals incur high costs
- Unlike a true free market, regulation causes increases in costs and decreases competition among insurers
I'm firmly on the side of moving towards the free market. (And I say that as someone living under a single payer system now.) Here's what I would do:
- Get rid of tax incentives that make health insurance tied to your employer, giving individuals back proper freedom of choice.
- Reduce regulations significantly.
-
In the short term, some people will still get rejected claims and other obnoxious behavior from insurance companies. We address that in two ways:
- Due to reduced regulations, new insurance companies will be able to enter the market offering more reliable coverage and better rates, and people will flock to them because they have the freedom to make their own choices.
- Sue the asses off of companies that reject claims unfairly. And ideally, as one of the few legitimate roles of government in all this, institute new laws that limit the ability of fine print to allow insurers to escape their responsibilities. (I'm hesitant that the latter will happen due to the incestuous relationship between Congress/regulators and insurers, but I can hope.)
Will this magically fix everything overnight like politicians normally promise? No. But it will allow the market to return to a healthy state. And I don't think it will take long (order of magnitude: 5-10 years) for it to come together, but that's just speculation.
And since there's a high correlation between those who believe government can fix problems by taking more control and demanding that only credentialed experts weigh in on a topic (both points I strongly disagree with BTW): I'm a trained actuary and worked in the insurance industry, and have directly seen how government regulation reduces competition, raises prices, and harms consumers.
And my final point: I don't think any prior art would be a good comparison for deregulation in the US, it's such a different market than any other country in the world for so many reasons that lessons wouldn't really translate. Nonetheless, I asked Grok for some empirical data on this, and at best the results of deregulation could be called "mixed," but likely more accurately "uncertain, confused, and subject to whatever interpretation anyone wants to apply."
https://x.com/i/grok/share/Zc8yOdrN8lS275hXJ92uwq98M
-
 @ 91bea5cd:1df4451c
2025-02-04 17:24:50
@ 91bea5cd:1df4451c
2025-02-04 17:24:50Definição de ULID:
Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível.
Gerar ULID
```sql
CREATE EXTENSION IF NOT EXISTS pgcrypto;
CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\000\000\000\000\000\000'; output TEXT = '';
unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER);
-- 10 entropy bytes ulid = timestamp || gen_random_bytes(10);
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ```
ULID TO UUID
```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF;
v = regexp_split_to_array(ulid, '');
-- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]);
-- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]);
RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE;
CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ```
UUID to ULID
```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ```
Gera 11 Digitos aleatórios: YBKXG0CKTH4
```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto;
-- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT;
-- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars;END; $$ LANGUAGE plpgsql; ```
Exemplo de USO
```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL );
-- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ```
Fontes
- https://github.com/scoville/pgsql-ulid
- https://github.com/geckoboard/pgulid
-
 @ 866e0139:6a9334e5
2025-03-24 10:51:52
@ 866e0139:6a9334e5
2025-03-24 10:51:52Autor: Milosz Matuschek. Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
Seit Sonntag (zu allem Glück auch noch meinem 45. Geburtstag) ist bei mir noch ein bisschen mehr los als sonst – und das liegt an Ihnen. Der Aufruf zur Gründung der „Friedenstaube“, einer unzensierbaren Friedenspublikation mit bekannten Stimmen aus der kritischen Szene, der Friedensbewegung und von Bürgerjournalisten ist bei Ihnen auf mehr als nur offene Ohren gestoßen! Ich bin regelrecht geplättet von den vielen Reaktionen, die ich noch gar nicht alle beantworten konnte.
Ich danke Ihnen herzlich für das Vertrauen in mich (auch wenn ich natürlich stark auf die Autoren angewiesen bin) und die überwältigenden Reaktionen: Es sind hunderte Abonnements für den Newsletter eingegangen, darunter einige bezahlte Abos und Förderabos und auch die ersten Genossenschaftsanteile wurden gezeichnet! Was mich besonders freut: Gut zehn weitere freiwillige Autoren wollen mitmachen und arbeiten bereits an den ersten Texten. Damit darf ich schon jetzt verkünden, dass die Genossenschaft definitiv gegründet werden kann, die Friedenstaube wird fliegen. Wie hoch und wie weit, das liegt dann nun nur noch in unser aller Hände.
Der Anfang ist jedenfalls gemacht. Die nächsten Wochen werden besonders arbeitsintensiv, ich bitte Sie um etwas Geduld: Aufbau einer Kernredaktion, Organisation der Abläufe, technologische Entwicklungsarbeiten, Genossenschaftsgründung etc. stehen jetzt auf der Agenda. Mit Tom-Oliver Regenauer darf ich den ersten Autor im redaktionellen Kernteam verkünden, der sich nicht nur große Verdienste im Schreiben erarbeitet hat (siehe u.a. sein Buch Hopium) sondern auch über Managementerfahrung verfügt; mit weiteren helfenden Händen bin ich im Gespräch.
Ich freue mich auf die (auch für mich) neue Erfahrung, quasi aus dem Nichts eine Publikation mit Redaktionsbetrieb und freien Autoren auf einer gänzlich neuen technologischen Infrastruktur aufzubauen. Es wäre illusorisch zu glauben, dass alles glatt gehen wird, denn wir starten quasi „on the go“, aber im Fall von Frieden oder Krieg gilt es, keine Zeit verstreichen zu lassen. Ich arbeite nach dem Motto „Tun, statt reden; zeigen, statt ankündigen; liefern, statt versprechen“.
Die ersten Texte zum Thema Frieden sind bereits publiziert, ein halbwegs geordneter Betrieb sollte ab April realistisch sein. Die Liste der Autoren wird regelmäßig aktualisiert, schauen Sie gerne hier (oder noch besser: hier) immer wieder herein. Dort finden Sie auch noch mal alle Infos, wenn Sie die Friedenstaube unterstützen wollen. Ab 1000 Euro/CHF werden Sie Genossenschafter, also Verleger!**
Auch an die bisherigen Unterstützer des Pareto-Projekts, der technologischen Basis der Friedenstaube, will ich hiermit schon etwas zurückgeben: Alle Spender für Pareto werden die Friedenstaube immer kostenlos lesen können. Sie, die Leser dieser Publikation haben die technologische Basis mit aufgebaut, die uns zur weltweit ersten, zensursicheren Friedenspublikation macht. Uns Autoren steht damit ein kompetentes Support-Team von inzwischen über zehn Entwicklern (und weiteren Helfern) an der Seite, welche die Friedenstaube am Fliegen halten werden.
Kontaktieren Sie mich gerne zu allen Fragen (je kürzer die Mail, desto früher kommt die Antwort): milosz\@pareto.space oder kontakt\@idw-europe.org
JETZT ABONNIEREN:
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel in Ihr Postfach, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht).
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF/EURO werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):
Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie mich an: milosz@pareto.space oder kontakt@idw-europe.org.
Was bewegt mich beim Thema Krieg und Frieden?
Erlauben Sie mir einen kurzen persönlichen Prolog: Ich stamme aus Schlesien. Mein Urgroßvater kämpfte im I. Weltkrieg bei Verdun. Mein Großvater wurde in die Wehrmacht eingezogen, kämpfte im Partisanenkrieg in Jugoslawien, verlor Hand und Auge. Ein Bruder meiner Großmutter entzog sich und landete in Dachau. Ich kenne meine Familiengeschichte nur in groben Umrissen, vielen wird es ähnlich gehen. Einige meiner schlesischen Vorfahren waren später vor allem Lokführer. Aufgrund der bewegten schlesischen Geschichte wechselten sie mehrfach die Uniform. Die Tätigkeit und Fahrstrecke blieb die gleiche. Für wen oder was kämpften sie in Kriegen in welchen Uniformen? Vermutlich wussten sie es selbst nicht.
Auch ich könnte heute nicht genau sagen, welche Interessen und Mächte die Kriegsmaschinerie bedienen. Doch ich wüsste es gerne und Sie vielleicht auch. Kämpfen ohne letztlich zu wissen für wen und warum: Wozu? Krieg simuliert Sinn und Notwendigkeit und lässt einen am Ende mit den großen Fragen allein, ahnungslos gestorben im Schützengraben. Zivilisatorisch ist das ein Offenbarungseid.
Bin ich ein totaler Anti-Militarist? Ich glaube nicht. Ich habe nichts gegen die Idee privaten Waffenbesitzes. Ich kann der Idee der Landesverteidigung durchaus etwas abgewinnen. Den Wehrdienst habe ich bewusst nicht verweigert. Ich wollte die Erfahrung machen. Hier schreibt also auch ein Obergefreiter a. D. eines bayerischen Gebirgspionierbataillons bei Rosenheim mit bronzener Schützenschnur, der am MG durchaus treffsicher war. Aber eben auch jemand, den der Wehrdienst zum Teil-Pazifisten gemacht hat. Mir war nach dem Grundwehrdienst klar: Wir sind eine Gurkentruppe, reines Kanonenfutter. 20-jährige Grünschnäbel mit zu viel Testosteron und Hollywood in den Gliedern, aber wenig Ahnung.
Ich war also einer, der sich verlässlich mit anderen beim Orientierungslauf im Wald verirrte; einer, der mit anderen übermüdet beim ersten Wachdienst einpennte (und damit im Ernstfall den Tod im Schlaf kennengelernt hätte, denn just erfolgte ein simulierter „Angriff“); einer, der auch mal übernächtigt sein Gewehr vor dem Zelt vergaß (wir sollten dem G3 den Namen unserer damaligen Freundin geben – wie pervers – ich vergaß also „Petra“ vor dem Zelt) und schließlich einer, der die meiste Zeit des Dienstes fürs Vaterland letztlich mit dem Servieren von Getränken und Schinkennudeln im Offizierskasino verbrachte und die institutionalisierten Alkoholiker der Bundeswehr bei Laune hielt („it ain’t much, but it was honest work“).
Anders gesagt: Krieg – spätestens seitdem: ohne mich. Auch wenn ich gerne Ernst Jünger lese und zitiere (er war einfach ein großartiger Chronist und lebendiger Geist), seinen abenteuerlustigen Militarismus kreide ich ihm an und rufe ihm posthum hinterher: man muss nicht erst einen Sohn im Krieg verloren haben, um zum Pazifisten zu werden.
Weitere Störgefühle tauchten auf: In meiner Dissertation durfte ich mich u.a. mit philosophischen Theorien zum Gesellschaftsvertrag (u.a. Kant, Rousseau, Locke und Hobbes sind hier zu nennen) beschäftigen. Dies brachte mein Staatsverständnis gerade bei der Kriegsfrage noch mehr durcheinander. Wenn Mindestziel der Staatsgründung innere und äußere Sicherheit sind, aber letztlich nicht der Staat den Bürger, sondern der Bürger den Staat schützt, wozu sich dann eine Schutzmacht erfinden, die einen am Ende durch den Fleischwolf jagt? Hobbes setzte zumindest auf Söldner.
Kriege werden mit Lügen begonnen, wusste Julian Assange. Können Sie mit Wahrheit beendet oder gar verhindert werden? Seit Walter Lippmanns „Liberty and the News“ von 1920 weiß man spätestens, dass gesicherte Information im Krieg das seltenste Gut ist. Sagt Lippmann als oberster Mainstream-Journalist und Einflüsterer der Mächtigen. Jeder Journalist muss hier ein Störgefühl entwickeln, der Leser noch mehr. Der Journalist der Nachrichtenagentur ist selten im Geschehen sondern wird vom heimischen Militär gebrieft, sein Bericht landet dann in den Newstickern und Redaktionen. Die Kriegsmaschinerie produziert also auch ihre eigene Sicht auf die Dinge, die sie den Bürgern als die Realität verkauft.
Kein Wunder, dass jede abweichende Information massiv bekämpft werden muss. Im Krieg ist Zweifel gleich Verrat, quasi unsolidarisches Sektierertum und Wehrkraftzersetzung, wenn nicht Feindbegünstigung. Der kritische Journalist steht in Ausnahmezuständen, wie man schon bei Corona sehen konnte, automatisch aus Staatssicht im Lager des Feindes und wird entsprechend behandelt. Zensursicheres Publizieren ist dann nicht nur ein nettes feature, sondern notwendige Basisvoraussetzung. Vor kurzem war Twitter/X nicht mehr zugänglich wegen massiven Cyberattacken. Wenn dann noch Rundfunk und Presse auf der Propagandawelle surfen und die Plattformzensur wieder zuschlägt, wird das Angebot schnell dünn.
Wem aber dient Zensur und Propaganda? Die aktuelle Lage im Russland-Ukraine-Konflikt ist auch Gelegenheit, um zu zeigen: Es sind eben nicht nur staatliche Interessen, die hier verhandelt werden, sondern es muss (wieder mal) eine andere Entität mit am Tisch sitzen, man nenne sie Deep State oder wie auch immer. Europäische Eliten dienen offensichtlich Fremdinteressen, wenn sie mit Aufrüstungsplänen Volksvermögen verspekulieren oder darin (wie von der Leyen) ein notwendiges „Investment“ sehen. Von wem werden wir letztlich regiert? Auch diesem Themen-Komplex werde ich mich in der Friedenstaube nähern.
Es gibt viel zu tun, aber für mich ist klar: Frieden ist ohne Wahrheit nicht zu bekommen, deshalb ist Wahrheitssuche auch immer Friedenssuche, wie Wahrheitsliebe letztlich Friedensliebe ist.
Gerade fallen auch im Mainstream die Corona-Lügen zur Labortheorie in sich zusammen, fünf Jahre nach Ausrufung der Pandemie. Der Frieden hat nur eine Chance, wenn es uns gelingt, die Lügen nun möglichst synchron zu den Geschehnissen aufzudecken und zu dokumentieren.
Das ist mein persönlicher Wunsch, mit dem ich die Friedenstaube fliegen lasse.
Was ist Ihrer? Schreiben Sie es gerne in die Kommentare. Welche Erwartungen, Wünsche haben Sie an uns? Liebe Autoren: Was ist euer Beweggrund, für den Frieden zur Feder zu greifen?
Zeichnen Sie jetzt “Friedensanleihen”. Werden Sie Genossenschafter und Verleger der Friedenstaube ab 1000 Euro/CHF. Es können mehrere Anteile pro Person gezeichnet werden, es bleibt bei einem Stimmrecht pro Kopf. milosz\@pareto.space
P.S: Mit diesem Text testen wir die Newsletterfunktion erstmals an mehrere Hundert Mailadressen. Wenn Sie die Friedenstaube abonniert haben, sollten Sie diesen Artikel per Mail bekommen haben.
ANZEIGE:
Sie suchen nach dem einfachsten Weg, Bitcoin zu kaufen und selbst zu verwahren?* Die* Relai-App ist Europas erfolgreichste Bitcoin-App.* Hier kaufen Sie Bitcoin in wenigen Schritten und können auch Sparpläne einrichten. Niemand hat Zugriff auf Ihre Bitcoin, außer Sie selbst.* Relai senkt jetzt die Gebühr auf 1%, mit dem Referral-Code MILOSZ sparen Sie weitere 10%. (keine Finanzberatung). Disclaimer wg. EU-Mica-Regulierung: Die Dienste von Relai werden ausschließlich für Einwohner der Schweiz und Italiens empfohlen.
Join the marketplace of ideas! We are building a publishing ecosystem on Nostr for citizen-journalism, starting with a client for blogging and newsletter distribution. Sound money and sound information should finally be in the hands of the people, right? Want to learn more about the Pareto Project? Zap me, if you want to contribute (all Zaps go to the project).
Are you a publication or journalist and want to be part of it, test us, migrate your content to Nostr? Write to team@pareto.space**
Not yet on Nostr and want the full experience? Easy onboarding via Start.
Pareto has started a crowdfunding campaign on Geyser. We were in the Top 3 in February, thank you for the support!
-
 @ 866e0139:6a9334e5
2025-03-24 10:50:59
@ 866e0139:6a9334e5
2025-03-24 10:50:59Autor: Ludwig F. Badenhagen. Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
Einer der wesentlichen Gründe dafür, dass während der „Corona-Pandemie“ so viele Menschen den Anweisungen der Spitzenpolitiker folgten, war sicher der, dass diese Menschen den Politikern vertrauten. Diese Menschen konnten sich nicht vorstellen, dass Spitzenpolitiker den Auftrag haben könnten, die Bürger analog klaren Vorgaben zu belügen, zu betrügen und sie vorsätzlich (tödlich) zu verletzen. Im Gegenteil, diese gutgläubigen Menschen waren mit der Zuversicht aufgewachsen, dass Spitzenpolitiker den Menschen dienen und deren Wohl im Fokus haben (müssen). Dies beteuerten Spitzenpolitiker schließlich stets in Talkshows und weiteren Medienformaten. Zwar wurden manche Politiker auch bei Fehlverhalten erwischt, aber hierbei ging es zumeist „nur“ um Geld und nicht um Leben. Und wenn es doch einmal um Leben ging, dann passieren die Verfehlungen „aus Versehen“, aber nicht mit Vorsatz. So oder so ähnlich dachte die Mehrheit der Bürger.
Aber vor 5 Jahren änderte sich für aufmerksame Menschen alles, denn analog dem Lockstep-Szenario der Rockefeller-Foundation wurde der zuvor ausgiebig vorbereitete Plan zur Inszenierung der „Corona-Pandemie“ Realität. Seitdem wurde so manchem Bürger, der sich jenseits von Mainstream-Medien informierte, das Ausmaß der unter dem Vorwand einer erfundenen Pandemie vollbrachten Taten klar. Und unverändert kommen täglich immer neue Erkenntnisse ans Licht. Auf den Punkt gebracht war die Inszenierung der „Corona-Pandemie“ ein Verbrechen an der Menschheit, konstatieren unabhängige Sachverständige.
Dieser Beitrag befasst sich allerdings nicht damit, die vielen Bestandteile dieses Verbrechens (nochmals) aufzuzählen oder weitere zu benennen. Stattdessen soll beleuchtet werden, warum die Spitzenpolitiker sich so verhalten haben und ob es überhaupt nach alledem möglich ist, der Politik jemals wieder zu vertrauen? Ferner ist es ein Anliegen dieses Artikels, die weiteren Zusammenhänge zu erörtern. Und zu guter Letzt soll dargelegt werden, warum sich der große Teil der Menschen unverändert alles gefallen lässt.
Demokratie
Von jeher organisierten sich Menschen mit dem Ziel, Ordnungsrahmen zu erschaffen, welche wechselseitiges Interagieren regeln. Dies führte aber stets dazu, dass einige wenige alle anderen unterordneten. Der Grundgedanke, der vor rund 2500 Jahren formulierten Demokratie, verfolgte dann aber das Ziel, dass die Masse darüber entscheiden können soll, wie sie leben und verwaltet werden möchte. Dieser Grundgedanke wurde von den Mächtigen sowohl gehasst als auch gefürchtet, denn die Gefahr lag nahe, dass die besitzlosen Vielen beispielsweise mit einer schlichten Abstimmung verfügen könnten, den Besitz der Wenigen zu enteignen. Selbst Sokrates war gegen solch eine Gesellschaftsordnung, da die besten Ideen nicht durch die Vielen, sondern durch einige wenige Kluge und Aufrichtige in die Welt kommen. Man müsse die Vielen lediglich manipulieren und würde auf diese Weise quasi jeden Unfug umsetzen können. Die Demokratie war ein Rohrkrepierer.
Die Mogelpackung „Repräsentative Demokratie“
Erst im Zuge der Gründung der USA gelang der Trick, dem Volk die „Repräsentative Demokratie“ unterzujubeln, die sich zwar nach Demokratie anhört, aber mit der Ursprungsdefinition nichts zu tun hat. Man konnte zwischen zwei Parteien wählen, die sich mit ihren jeweiligen Versprechen um die Gunst des Volkes bewarben. Tatsächlich paktierten die Vertreter der gewählten Parteien (Politiker) aber mit den wirklich Mächtigen, die letztendlich dafür sorgten, dass diese Politiker in die jeweiligen exponierten Positionen gelangten, welche ihnen ermöglichten (und somit auch den wirklich Mächtigen), Macht auszuüben. Übrigens, ob die eine oder andere Partei „den Volkswillen“ für sich gewinnen konnte, war für die wirklich Mächtigen weniger von Bedeutung, denn der Wille der wirklich Mächtigen wurde so oder so, wenn auch in voneinander differierenden Details, umgesetzt.
Die Menschen waren begeistert von dieser Idee, denn sie glaubten, dass sie selbst „der Souverän“ seien. Schluss mit Monarchie sowie sonstiger Fremdherrschaft und Unterdrückung.
Die Mächtigen waren ebenfalls begeistert, denn durch die Repräsentative Demokratie waren sie selbst nicht mehr in der Schusslinie, weil das Volk sich mit seinem Unmut fortan auf die Politiker konzentrierte. Da diese Politiker aber vielleicht nicht von einem selbst, sondern von vielen anderen Wahlberechtigten gewählt wurden, lenkte sich der Groll der Menschen nicht nur ab von den wirklich Mächtigen, sondern auch ab von den Politikern, direkt auf „die vielen Idioten“ aus ihrer eigenen Mitte, die sich „ver-wählt“ hatten. Diese Lenkung des Volkes funktionierte so hervorragend, dass andere Länder die Grundprinzipien dieses Steuerungsinstrumentes übernahmen. Dies ist alles bei Rainer Mausfeld nachzulesen.
Ursprünglich waren die Mächtigen nur regional mächtig, sodass das Führen der eigenen Menschen(vieh)herde eher eine lokale Angelegenheit war. Somit mussten auch nur lokale Probleme gelöst werden und die Mittel zur Problemlösung blieben im eigenen Problembereich.
JETZT ABONNIEREN:
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel in Ihr Postfach, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht).
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF/EURO werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):
Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: milosz@pareto.space oder kontakt@idw-europe.org.
Beherrschungsinstrumente der globalen Massenhaltung
Im Zuge der territorialen Erweiterungen der „Besitzungen“ einiger wirklich Mächtiger wurden die Verwaltungs- und Beherrschungsinstrumente überregionaler. Und heute, zu Zeiten der globalen Vernetzung, paktieren die wirklich Mächtigen miteinander und beanspruchen die Weltherrschaft. Längst wird offen über die finale Realisierung einen Weltregierung, welche die Nationalstaaten „nicht mehr benötigt“, gesprochen. Dass sich Deutschland, ebenso wie andere europäische Staaten, der EU untergeordnet hat, dürfte auch Leuten nicht entgangen sein, die sich nur über die Tagesschau informieren. Längst steht das EU-Recht über dem deutschen Recht. Und nur kurze Zeit ist es her, als die EU und alle ihre Mitgliedsstaaten die WHO autonom darüber entscheiden lassen wollten, was eine Pandemie ist und wie diese für alle verbindlich „bekämpft“ werden soll. Eine spannende Frage ist nun, wer denn über der EU und der WHO sowie anderen Institutionen steht?
Diese Beschreibung macht klar, dass ein „souveränes Land“ wie das unverändert von der amerikanischen Armee besetzte Deutschland in der Entscheidungshierarchie an die Weisungen übergeordneter Entscheidungsorgane gebunden ist. An der Spitze stehen - wie kann es anders sein - die wirklich Mächtigen.
Aber was nützt es dann, Spitzenpolitiker zu wählen, wenn diese analog Horst Seehofer nichts zu melden haben? Ist das Wählen von Politikern nicht völlig sinnlos, wenn deren Wahlversprechen ohnehin nicht erfüllt werden? Ist es nicht so, dass die Menschen, welche ihre Stimme nicht behalten, sondern abgeben, das bestehende System nur nähren, indem sie Wahlergebnisse akzeptieren, ohne zu wissen, ob diese manipuliert wurden, aber mit der Gewissheit, dass das im Zuge des Wahlkampfes Versprochene auf keinen Fall geliefert wird? Aktive Wähler glauben trotz allem an die Redlichkeit und Wirksamkeit von Wahlen, und sie akzeptieren Wahlergebnisse, weil sie denken, dass sie von „so vielen Idioten, die falsch wählen“, umgeben sind, womit wir wieder bei der Spaltung sind. Sie glauben, der Stand des aktuellen Elends sei „selbst gewählt“.
Die Wahl der Aufseher
Stellen Sie sich bitte vor, Sie wären im Gefängnis, weil Sie einen kritischen Artikel mit „gefällt mir“ gekennzeichnet haben oder weil Sie eine „Kontaktschuld“ trifft, da in Ihrer Nachbarschaft ein „verschwörerisches Symbol“ von einem „aufmerksamen“ Nachbarn bei einer „Meldestelle“ angezeigt wurde oder Sie gar eine Tat, „unterhalb der Strafbarkeitsgrenze“ begangen hätten, dann würden Sie möglicherweise mit Maßnahmen bestraft, die „keine Folter wären“. Beispielsweise würde man Sie während Ihrer „Umerziehungshaft“ mit Waterboarding, Halten von Stresspositionen, Dunkelhaft etc. dabei „unterstützen“, „Ihre Verfehlungen zu überdenken“. Stellen Sie sich weiterhin vor, dass Sie, so wie alle anderen Inhaftierten, an der alle vier Jahre stattfindenden Wahl der Aufseher teilnehmen könnten, und Sie hätten auch einen Favoriten, der zwar Waterboarding betreibt, aber gegen alle anderen Maßnahmen steht. Sie hätten sicher allen Grund zur Freude, wenn Sie Ihren Kandidaten durchbringen könnten, oder? Aber was wäre, wenn der Aufseher Ihrer Wahl dann dennoch alle 3 „Nicht-Folter-Maßnahmen“ anwenden würde, wie sämtliche anderen Aufseher zuvor? Spätestens dann müssten Sie sich eingestehen, dass es der Beruf des Aufsehers ist, Aufseher zu sein und dass er letztendlich tut, was ihm „von oben“ aufgetragen wird. Andernfalls verliert er seinen Job. Oder er verunfallt oder gerät in einen Skandal etc. So oder so, er verliert seinen Job - und den erledigt dann ein anderer Aufseher.
Die Wahl des Aufsehers ändert wenig, solange Sie sich im System des Gefängnisses befinden und der Aufseher integraler Bestandteil dieses Systems ist. Zur Realisierung einer tatsächlichen Änderung müssten Sie dort herauskommen.
Dieses Beispiel soll darstellen, dass alles in Hierarchien eingebunden ist. Die in einem System eingebundenen Menschen erfüllen ihre zugewiesenen Aufgaben, oder sie werden bestraft.
Das aktuelle System schadet dem Volk
Auch in der staatlichen Organisation von Menschen existieren hierarchische Gliederungen. Eine kommunale Selbstverwaltung gehört zum Kreis, dieser zum Land, dieses zum Staat, dieser zur EU, und diese - zu wem auch immer. Und vereinnahmte Gelder fließen nach oben. Obwohl es natürlich wäre, dass die Mittel dorthin fließen, wo sie der Allgemeinheit und nicht einigen wenigen dienen, also nach unten.
Warum muss es also eine Weltregierung geben? Warum sollen nur einige Wenige über alle anderen bestimmen und an diesen verdienen (Nahrung, Medikamente, Krieg, Steuern etc.)? Warum sollen Menschen, so wie Vieh, das jemandem „gehört“, mit einem Code versehen und bereits als Baby zwangsgeimpft werden? Warum müssen alle Transaktionen und sämtliches Verhalten strickt gesteuert, kontrolliert und bewertet werden?
Viele Menschen werden nach alledem zu dem Schluss kommen, dass solch ein System nur einigen wenigen wirklich Mächtigen und deren Helfershelfern nützt. Aber es gibt auch eine Gruppe Menschen, für die im Land alles beanstandungsfrei funktioniert. Die Spaltung der Menschen ist perfekt gelungen und sofern die eine Gruppe darauf wartet, dass die andere „endlich aufwacht“, da die Fakten doch auf dem Tisch liegen, so wird sie weiter warten dürfen.
Julian Assange erwähnte einst, dass es für ihn eine unglaubliche Enttäuschung war, dass ihm niemand half. Assange hatte Ungeheuerlichkeiten aufgedeckt. Es gab keinen Aufstand. Assange wurde inhaftiert und gefoltert. Es gab keinen Aufstand. Assange sagte, er hätte nicht damit gerechnet, dass die Leute „so unglaublich feige“ seien.
Aber womit rechnete er den stattdessen? Dass die Massen „sich erheben“. Das gibt es nur im Film, denn die Masse besteht aus vielen maximal Indoktrinierten, die sich wie Schafe verhalten, was als Züchtungserfolg der Leute an den Schalthebeln der Macht und deren Herren, den wirklich Mächtigen, anzuerkennen ist. Denn wer mächtig ist und bleiben möchte, will sicher keine problematischen Untertanen, sondern eine gefügige, ängstliche Herde, die er nach Belieben ausbeuten und steuern kann. Wenn er hierüber verfügt, will er keinen Widerstand.
Ob Corona, Krieg, Demokratie- und Klimarettung oder Meinungsäußerungsverbote und Bürgerrechte, die unterhalb der Strafbarkeitsgrenze liegen, all diese und viele weitere Stichworte mehr sind es, die viele traurig und so manche wütend machen.
Auch das Mittel des Demonstrierens hat sich als völlig wirkungslos erwiesen. Die vielen gruseligen Videoaufnahmen über die massivsten Misshandlungen von Demonstranten gegen die Corona-Maßnahmen führen zu dem Ergebnis, dass die Exekutive ihr Gewaltmonopol nutzt(e), um die Bevölkerung gezielt zu verletzen und einzuschüchtern. Bekanntlich kann jede friedliche Demonstration zum Eskalieren gebracht werden, indem man Menschen in die Enge treibt (fehlender Sicherheitsabstand) und einige V-Leute in Zivil mit einschlägigen Flaggen und sonstigen „Symbolen“ einschleust, die für Krawall sorgen, damit die gepanzerten Kollegen dann losknüppeln und die scharfen Hunde zubeißen können. So lauten zumindest die Berichte vieler Zeitzeugen und so ist es auch auf vielen Videos zu sehen. Allerdings nicht im Mainstream.
Dieses Vorgehen ist deshalb besonders perfide, weil man den Deutschen ihre Wehrhaftigkeit aberzogen hat. Nicht wehrfähige Bürger und eine brutale Staatsmacht mit Gewaltmonopol führen zu einem Gemetzel bei den Bürgern.
Ähnliches lässt sich auch in zivilen Lebenssituationen beobachten, wenn die hiesige zivilisierte Bevölkerung auf „eingereiste“ Massenvergewaltiger und Messerstecher trifft, die über ein anderes Gewalt- und Rechtsverständnis verfügen als die Einheimischen.
System-Technik
Die These ist, dass es eine Gruppe von global agierenden Personen gibt, welche das Geschehen auf der Erde zunehmend wirksam zu ihrem individuellen Vorteil gestaltet. Wie sich diese Gruppe definiert, kann bei John Coleman (Das Komitee der 300) und David Icke nachgelesen werden. Hierbei handelt es ich um Autoren, die jahrzehntelang analog streng wissenschaftlichen Grundlagen zu ihren Themen geforscht haben und in ihren jeweiligen Werken sämtliche Quellen benennen. Diese Autoren wurden vom Mainstream mit dem Prädikatsmerkmal „Verschwörungstheoretiker“ ausgezeichnet, wodurch die Ergebnisse Ihrer Arbeiten umso glaubwürdiger sind.
Diese mächtige Gruppe hat mit ihren Schergen nahezu den gesamten Planeten infiltriert, indem sie Personen in führenden Positionen in vielen Belangen größtmögliche Freiheiten sowie Schutz gewährt, aber diesen im Gegenzug eine völlige Unterwerfung bei Kernthemen abfordert. Die Motivatoren für diese Unterwerfung sind, abgesehen von materiellen Zuwendungen, auch „Ruhm und Ehre sowie Macht“. Manchmal wird auch Beweismaterial für begangene Verfehlungen (Lolita-Express, Pizzagate etc.) genutzt, um Forderungen Nachdruck zu verleihen. Und auch körperliche Bestrafungen der betroffenen Person oder deren Angehörigen zählen zum Repertoire der Motivatoren. Letztendlich ähnlich den Verhaltensweisen in einem Mafia-Film.
Mit dieser Methodik hat sich diese mächtige Gruppe im Laufe von Jahrhunderten! eine Organisation erschaffen, welche aus Kirchen, Parteien, Firmen, NGO, Vereinen, Verbänden und weiteren Organisationsformen besteht. Bestimmte Ämter und Positionen in Organisationen können nur von Personen eingenommen und gehalten werden, die „auf Linie sind“.
Die Mitglieder der Gruppe tauchen in keiner Rubrik wie „Die reichsten Menschen der Welt“ auf, sondern bleiben fern der Öffentlichkeit. Wer jemanden aus ihren Reihen erkennt und beschuldigt, ist ein „Antisemit“ oder sonstiger Übeltäter und wird verfolgt und bekämpft. Über mächtige Vermögensverwaltungskonzerne beteiligen sich die Mitglieder dieser Gruppe anonym an Unternehmen in Schlüsselpositionen in einer Dimension, die ihnen wesentlichen Einfluss auf die Auswahl der Topmanager einräumt, sodass die jeweilige Unternehmenspolitik nach Vorgaben der Gruppe gestaltet wird.
Die Gruppe steuert das Geldsystem, von dem sich der Planet abhängig zu sein wähnt. Hierzu eine Erläuterung: Ein Staat wie Deutschland ist bekanntlich maximal verschuldet. Man stelle sich vor, ein unliebsamer Politiker würde entgegen sämtlicher „Brandmauern“ und sonstiger Propaganda und Wahlmanipulationen gewählt, das Land zu führen, dann könnte dieser keine Kredit über 500 Mrd. Euro bei der nächsten Sparkasse beantragen, sondern wäre auf die Mächtigen dieser Welt angewiesen. Jeder weiß, dass Deutschland als Staat kein funktionierendes Geschäftsmodell hat und somit nicht in der Lage ist, solch ein Darlehen zurückzuzahlen. Welche Motivation sollte also jemand haben, einem Land wie Deutschland so viel Geld ohne Aussicht auf Rückführung zu geben? Es leuchtet ein, dass dieser Politiker andere Gefälligkeiten anbieten müsste, um das Darlehen zu bekommen. Im Falle einer Weigerung zur Kooperation könnte der Staatsapparat mit seinen Staatsdienern, Bürgergeld- und Rentenempfänger etc. nicht mehr bezahlt werden und dieser Politiker wäre schnell wieder weg. Er würde medial hingerichtet. Es ist somit davon auszugehen, dass ein Spitzenpolitiker dieser Tage nicht über viele Optionen verfügt, denn er übernimmt eine Situation, die von seinen Vorgängern erschaffen wurde. Trotz alledem darauf zu hoffen, dass es einen anderen Politiker geben könnte, mit dem dann alles wieder gut wird, mutet ziemlich infantil an.
Dass ein Großteil der Medien von Zuwendungen abhängig ist, dürfte ebenfalls leicht nachzuvollziehen sein, denn der gewöhnliche Bürger zahlt nichts für den Content der MSM. Abhängig davon, von wem (Regierung, Philanthrop, Konzern etc.) ein Medium am Leben gehalten wird, gestalten sich auch dessen Inhalte. Und wenn angewiesen wird, dass ein Politiker medial hingerichtet werden soll, dann bedient die Maschinerie das Thema. Man beobachte einfach einmal, dass Politiker der Kartell-Parteien völlig anders behandelt werden als solche jenseits der „Brandmauer“. Und der Leser, der solche Auftragsarbeiten kostenlos liest, ist der Konsument, für dessen Indoktrination die Finanziers der Verlage gerne zahlen. Mittlerweile kann durch die Herrschaft über die Medien und die systematische Vergiftung der Körper und Geister der Population die öffentliche Meinung gesteuert werden. Die überwiegende Zahl der Deutschen scheint nicht mehr klar denken zu können.
Wer sich das aktuelle Geschehen in der deutschen Politik mit klarem Verstand ansieht, kommt nicht umhin, eine Fernsteuerung der handelnden Politiker in Betracht zu ziehen. Aber was soll daran verwundern? Sind es deshalb „böse Menschen“? Sind die in „Forschungslaboren“ arbeitenden Quäler von „Versuchstieren“ böse Menschen? Sind der Schlächter, der Folterer und der Henker böse Menschen? Oder der knüppelnde Polizist? Es handelt sich zunächst einmal um Personen, die einen Vorteil dadurch haben, Ihrer Tätigkeit nachzugehen. Sie sind integrale Bestandteile eines Belohnungssystems, welches von oben nach unten Anweisungen gibt. Und wenn diese Anweisungen nicht befolgt werden, führt dies für den Befehlsverweigerer zu Konsequenzen.
Der klare Verstand
Es ist nun eine spannende Frage, warum so viele Menschen sich solch eine Behandlung gefallen lassen? Nun, das ist relativ einfach, denn das angepasste Verhalten der Vielen ist nichts anderes als ein Züchtungserfolg der Wenigen.
Die Psyche der Menschen ist ebenso akribisch erforscht worden wie deren Körperfunktionen. Würden die Menschen von den wirklich Mächtigen geliebt, dann würde genau gewusst, wie sie zu behandeln und mit ihren jeweiligen Bedürfnissen zu versorgen sind. Stattdessen werden die Menschen aber als eine Einnahmequelle betrachtet. Dies manifestiert sich exemplarisch in folgenden Bereichen:
- Das Gesundheitssystem verdient nichts am gesunden Menschen, sondern nur am (dauerhaft) kranken, der um Schmerzlinderung bettelt. Bereits als Baby werden Menschen geimpft, was die jeweilige Gesundheit (mit Verweis auf die Werke von Anita Petek-Dimmer u. a.) nachhaltig negativ beeinflusst. Wer hat denn heute keine Krankheiten? Die „Experten“ des Gesundheitssystems verteufeln Vitamin D, Vitamin C, Lithium, die Sonne, Natur etc. und empfehlen stattdessen Präparate, die man patentieren konnte und mit denen die Hersteller viel Geld verdienen. Die Präparate heilen selten, sondern lindern bestenfalls zuvor künstlich erzeugte Leiden, und müssen oftmals dauerhaft eingenommen werden. Was ist aus den nicht Geimpften geworden, die alle sterben sollten? Sind diese nicht die einzigen Gesunden dieser Tage? Ist nicht jeder Geimpfte entweder permanent krank oder bereits tot? Abgesehen von denen, welche das Glück hatten, „Sonderchargen“ mit Kochsalz zu erhalten. \ \ Wem gehören die wesentlichen Player im Gesundheitswesen zu einem erheblichen Teil? Die Vermögensverwalter der wirklich Mächtigen.
- Ähnlich gestaltet es sich bei der Ernährungsindustrie. Die von dort aus verabreichten Produkte sind die Ursachen für den Gesundheitszustand der deutschen Population. Das ist aber auch irgendwie logisch, denn wer sich nicht falsch ernährt und gesund bleibt, wird kein Kunde des Gesundheitswesens. \ \ Die Besitzverhältnisse in der Ernährungsindustrie ähneln denen im Gesundheitswesen, sodass am gleichen Kunden gearbeitet und verdient wird.
- Die Aufzählung konnte nun über die meisten Branchen, in denen mit dem Elend der Menschen viel verdient werden kann, fortgesetzt werden. Waffen (BlackRock erhöhte beispielsweise seine Anteile an der Rheinmetall AG im Juni 2024 auf 5,25 Prozent. Der US-Vermögensverwalter ist damit der zweitgrößte Anteilseigner nach der französischen Großbank Société Générale.), Energie, Umwelt, Technologie, IT, Software, KI, Handel etc.
Wie genau Chemtrails und Technologien wie 5G auf den Menschen und die Tiere wirken, ist ebenfalls umstritten. Aber ist es nicht seltsam, wie krank, empathielos, antriebslos und aggressiv viele Menschen heute sind? Was genau verabreicht man der Berliner Polizei, damit diese ihre Prügelorgien auf den Rücken und in den Gesichtern der Menschen wahrnehmen, die friedlich ihre Demonstrationsrechte wahrnehmen? Und was erhalten die ganzen zugereisten „Fachkräfte“, die mit Ihren Autos in Menschenmengen rasen oder auch Kinder und Erwachsene niedermessern?
Das Titelbild dieses Beitrags zeigt einige Gebilde, welche regelmäßig bei Obduktionen von Geimpften in deren Blutgefäßen gefunden werden. Wie genau wirken diese kleinen Monster? Können wir Menschen ihr Unverständnis und ihr Nicht-Aufwachen vorwerfen, wenn wir erkennen, dass diese Menschen maximal vergiftet wurden? Oder sollten einfach Lösungen für die Probleme dieser Zeit auch ohne den Einbezug derer gefunden werden, die offenbar nicht mehr Herr ihrer Sinne sind?
Die Ziele der wirklich Mächtigen
Wer sich entsprechende Videosequenzen der Bilderberger, des WEF und anderen „Überorganisationen“ ansieht, der erkennt schnell das Muster:
- Reduzierung der Weltpopulation um ca. 80 Prozent
- Zusammenbruch der Wirtschaft, damit diese von den Konzernen übernommen werden kann.
- Zusammenbruch der öffentlichen Ordnung, um eine totale Entwaffnung und eine totale Überwachung durchsetzen zu können.
- Zusammenbruch der Regierungen, damit die Weltregierung übernehmen kann.
Es ist zu überdenken, ob die Weltregierung tatsächlich das für die Vielen beste Organisationssystem ist, oder ob die dezentrale Eigenorganisation der jeweils lokalen Bevölkerung nicht doch die bessere Option darstellt. Baustellen würden nicht nur begonnen, sondern auch schnell abgearbeitet. Jede Region könnte bestimmen, ob sie sich mit Chemtrails und anderen Substanzen besprühen lassen möchte. Und die Probleme in Barcelona könnte die Menschen dort viel besser lösen als irgendwelche wirklich Mächtigen in ihren Elfenbeintürmen. Die lokale Wirtschaft könnte wieder zurückkommen und mit dieser die Eigenständigkeit. Denn die den wirklich Mächtigen über ihre Vermögensverwalter gehörenden Großkonzerne haben offensichtlich nicht das Wohl der Bevölkerung im Fokus, sondern eher deren Ausbeutung.
Das Aussteigen aus dem System ist die wahre Herkulesaufgabe und es bedarf sicher Mut und Klugheit, sich dieser zu stellen. Die Politiker, die unverändert die Narrative der wirklich Mächtigen bedienen, sind hierfür denkbar ungeeignet, denn sie verfolgen kein Lebensmodell, welches sich von Liebe und Mitgefühl geleitet in den Dienst der Gesamtheit von Menschen, Tieren und Natur stellt.
Schauen Sie einmal genau hin, denken Sie nach und fühlen Sie mit.
Was tun?
Jedes System funktioniert nur so lange, wie es unterstützt wird. Somit stellt sich die Frage, wie viele Menschen das System ignorieren müssen, damit es kollabiert, und auf welche Weise dieses Ignorieren durchzuführen ist? Merkbar ist, dass die große Masse der Verwaltungsangestellten krank und oder unmotiviert und somit nicht wirksam ist. Würden die entsprechenden Stellen massiv belastet und parallel hierzu keine Einnahmen mehr realisieren, wäre ein Kollaps nah. Die Prügelpolizisten aus Berlin können nicht überall sein und normale Polizisten arbeiten nicht gegen unbescholtene Bürger, sondern sorgen sich selbst um ihre Zukunft. Gewalt ist sicher keine Lösung, und sicher auch nicht erforderlich.
Wie eine gerechte Verwaltungsform aufgebaut werden muss? Einfach so, wie sie in den hiesigen Gesetzen beschrieben steht. Aber eine solche Organisationsform muss frei sein von Blockparteien und korrupten Politikern und weisungsgebundenen Richtern etc. Stattdessen werden Menschen benötigt, welche die Menschen lieben und ihnen nicht schaden wollen. Außerdem sollten diese Führungspersonen auch wirklich etwas können, und nicht nur „Politiker“ ohne weitere Berufserfahrungen sein.
Ludwig F. Badenhagen (Pseudonym, Name ist der Redaktion bekannt).
Der Autor hat deutsche Wurzeln und betrachtet das Geschehen in Deutschland und Europa aus seiner Wahlheimat Südafrika. Seine Informationen bezieht er aus verlässlichen Quellen und insbesondere von Menschen, die als „Verschwörungstheoretiker“, „Nazi“, „Antisemit“ sowie mit weiteren Kampfbegriffen der dortigen Systemakteure wie Politiker und „Journalisten“ diffamiert werden. Solche Diffamierungen sind für ihn ein Prädikatsmerkmal. Er ist international agierender Manager mit einem globalen Netzwerk und verfügt hierdurch über tiefe Einblicke in Konzerne und Politik.
Not yet on Nostr and want the full experience? Easy onboarding via Start.
-
 @ 91bea5cd:1df4451c
2025-02-04 17:15:57
@ 91bea5cd:1df4451c
2025-02-04 17:15:57Definição de ULID:
Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível.
Gerar ULID
```sql
CREATE EXTENSION IF NOT EXISTS pgcrypto;
CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\000\000\000\000\000\000'; output TEXT = '';
unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER);
-- 10 entropy bytes ulid = timestamp || gen_random_bytes(10);
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ```
ULID TO UUID
```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF;
v = regexp_split_to_array(ulid, '');
-- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]);
-- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]);
RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE;
CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ```
UUID to ULID
```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ```
Gera 11 Digitos aleatórios: YBKXG0CKTH4
```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto;
-- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT;
-- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars;END; $$ LANGUAGE plpgsql; ```
Exemplo de USO
```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL );
-- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ```
Fontes
- https://github.com/scoville/pgsql-ulid
- https://github.com/geckoboard/pgulid
-
 @ 866e0139:6a9334e5
2025-03-24 10:50:16
@ 866e0139:6a9334e5
2025-03-24 10:50:16Autor: René Boyke, Rechtsanwalt. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier.
Frieden. Ein Begriff den jeder kennt, oder? Kennen schon. Aber was bedeutet er? Die Abwesenheit von Gewalt und Konflikten? Ja, auch, wenn man Frieden seinem Widerpart, dem Krieg, gegenüberstellt. Demnach müsste immer dann Frieden herrschen, wenn es keinen Krieg gibt. So richtig überzeugt das nicht, denn Frieden entsteht nicht aus heiterem Himmel. Er erfordert Verhandlungen, Toleranz und ganz allgemein die Förderung von Gerechtigkeit. Doch was verstehen wir unter Gerechtigkeit? Was unter Toleranz? Und wann verhandeln wir wirklich und ehrlich?
Das Grundgesetz als Friedensauftrag
Der Begriff des Friedens ist also unscharf und von weiteren unscharfen Begriffen abhängig. Und doch ist er Gegenstand des Recht z.B. des Grundgesetzes (GG):
- Nach der Präambel des GG verpflichtet sich das Deutsche Volk „dem Frieden der Welt zu dienen.“
- In Art. 1 Abs. 2 GG bekennt sich das Deutsche Volk zu den Menschenrechten als Grundlage des Friedens in der Welt.
- Art. 26 Abs. 1 GG verbietet Handlungen, die geeignet sind und in der Absicht vorgenommen werden, „das friedliche Zusammenleben der Völker zu stören.“
Der Frieden ist also unzweifelhaft Gegenstand des deutschen Rechts – und natürlich auch des Völkerrechts. Bereits in Art. 1 Ziff. 1 der VN-Charta ist zu lesen, dass ein gesetztes Ziel der Vereinten Nationen die Wahrung des Weltfriedens ist und dass sie „Bedrohungen des Friedens verhüten und beseitigen“ will. Es ist also festzustellen: Der Begriff des Friedens ist unscharf und damit unklar, aber dennoch ist er Teil des deutschen Rechts und auch des internationalen Völkerrechts. Bei dieser Sachlage ist Streit vorprogrammiert. Wenn nicht klar ist, was Frieden eigentlich ist, aber von seinem Vorliegen oder seiner Abwesenheit rechtliche Konsequenzen abhängen, dann wird dies selbst zu Auseinandersetzungen führen.
So meinen die einen, einen anderen Staat präventiv mit Waffengewalt anzugreifen, fördere den „Frieden“ – wir erinnern uns an den Präventivschlag der USA gegen den Irak 2003. Andere sehen darin nichts anderes als einen rechtswidrigen Angriffskrieg. Rechtliche Konsequenzen hatte dieser Angriffskrieg für die USA nicht. Blicken wir auf die Bewertung des Ukrainekriegs im Jahr 2022, der seitens 1/3 Russlands ebenfalls einen Präventivkrieg darstellt, ist festzustellen, dass es auch hier wieder geteilte Lager gibt.
JETZT ABONNIEREN:
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel in Ihr Postfach, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht).
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):
Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: milosz@pareto.space oder kontakt@idw-europe.org.
Die einen sehen das Verhaltens Russland als gerechtfertigt an, die anderen als völkerrechtswidrig. Interessanterweise halten viele, die den Angriffs der USA auf den Irak für gerechtfertigt hielten, den Angriff Russlands auf die Ukraine nicht für gerechtfertigt. Wie kann das sein? Werden hier unterschiedliche Kriterien angelegt? Warum gefährdet der Angriff der USA – die im Übrigen die Gründe für die Bedrohung des Iraks nachweislich erfunden und damit gelogen haben – angeblich nicht den Frieden, obwohl es ja nachweislich zum Krieg kam? Und warum soll das Verhalten Russlands den Frieden gefährden? Erscheint diese unterschiedliche Bewertung nicht völlig willkürlich?
Welche Begriffe für Frieden werden hier zugrunde gelegt? Der 2019 verstorbene ehemalige Richter am Bundesverwaltungsvewaltungsgericht, Dr. Dieter Deiseroth, hat in einem Aufsatz 2010 dargelegt, dass völlig unklar ist, was unter dem Begriff des Friedens zu verstehen ist. Deiseroth schrieb: „Für die Kompetenzen des UN-Sicherheitsrates ist damit der Friedensbegriff von\ entscheidender Bedeutung. Er ist in der UN-Charta nicht definiert. Das macht\ Probleme.“ Und: „Je weiter der Friedensbegriff ausgelegt wird, umso weiter gehen\ die Kompetenzen des UN-Sicherheitsrates (...).“
Ein Definitionsvakuum und ein Auftrag
Umfasst Frieden im rechtlichen Kontext lediglich die Abwesenheit zwischenstaatlicher bewaffneter Konflikte? Was ist mit Piraterie? Was mit Terrorakten? Raubbau an der Natur? Wer Frieden nicht definieren kann, der kann auch nicht sagen, wann er bedroht ist. Wenn man etwas bewahren will, dann sollte man doch wissen, was dieses Etwas ist, was man zu bewahren vorgibt, oder? Weiß man dies nicht, lässt sich selbst ein Angriff auf ein anderes Land als friedenssichernde Maßnahme verkaufen, während der Angriff eines anderen Landes plötzlich als rechtswidriger Friedensbruch gilt.
Der Willkür ist Tür und Tor geöffnet. Dann bestimmt der Stärkere bzw. dessen Propaganda, was Recht ist und was Unrecht. Das jedoch hat mit Recht nichts zu tun, bzw. sollte mit Recht nichts zu tun haben, denn es gehört leider auch zur Realität des Rechts, dass es der absolute Regelfall ist, dass der Stärkere seine einzelfallbezogene Definitionshoheit und damit sein „Recht“ durchsetzt und der Schwächere – mag er noch so gute Argumente haben – den Kürzeren zieht.
Doch diesem Sein folgt denklogisch kein Sollen. Dieser systemische Rechtsmissbrauch ist kein Argument dafür, diesen Zustand beizubehalten und ihn nicht anzuprangern. Er ist vielmehr Argument dafür, diesen Zustand offenzulegen, zu kritisieren und auf seine Beseitigung hinzuwirken.
Wie kann Frieden nun also definiert werden? So definiert, dass eben nicht eine Autorität seine eigene Definitionsmacht missbraucht? Meines Erachtens geht dies nur im gegenseitigen ehrlichen Austausch der Parteien. Der Frieden ist kein allgemein definierbarer Zustand, schon gar nicht ist er ein losgelöst von anderen Lebensbereichen existierender normativer Begriff. Die rechtliche Dimension des Friedensbegriffs kann nicht für sich allein stehen, sondern ist in eine Lebenswirklichkeit eingebettet, die bei jedem einzelnen in sich selbst als innerer Frieden beginnt – dieser Ursprung ist auch der Ursprung der rechtlichen Dimension des Friedensbegriffs.
Oder anders formuliert: Ohne inneren Frieden kein äußerer Frieden.
René Boyke ist Rechtsanwalt mit Schwerpunkt Asylrecht. Er hat sieben Jahre im Bundesamt für Migration und Flüchtlinge gearbeitet und betreibt die Seite covid-justiz.de auf der er Gerichtsentscheidungen aus der Coronazeit kommentiert.
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren, zappen etc.)? Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ e3ba5e1a:5e433365
2025-02-04 08:29:00
@ e3ba5e1a:5e433365
2025-02-04 08:29:00President Trump has started rolling out his tariffs, something I blogged about in November. People are talking about these tariffs a lot right now, with many people (correctly) commenting on how consumers will end up with higher prices as a result of these tariffs. While that part is true, I’ve seen a lot of people taking it to the next, incorrect step: that consumers will pay the entirety of the tax. I put up a poll on X to see what people thought, and while the right answer got a lot of votes, it wasn't the winner.

For purposes of this blog post, our ultimate question will be the following:
- Suppose apples currently sell for $1 each in the entire United States.
- There are domestic sellers and foreign sellers of apples, all receiving the same price.
- There are no taxes or tariffs on the purchase of apples.
- The question is: if the US federal government puts a $0.50 import tariff per apple, what will be the change in the following:
- Number of apples bought in the US
- Price paid by buyers for apples in the US
- Post-tax price received by domestic apple producers
- Post-tax price received by foreign apple producers
Before we can answer that question, we need to ask an easier, first question: before instituting the tariff, why do apples cost $1?
And finally, before we dive into the details, let me provide you with the answers to the ultimate question. I recommend you try to guess these answers before reading this, and if you get it wrong, try to understand why:
- The number of apples bought will go down
- The buyers will pay more for each apple they buy, but not the full amount of the tariff
- Domestic apple sellers will receive a higher price per apple
- Foreign apple sellers will receive a lower price per apple, but not lowered by the full amount of the tariff
In other words, regardless of who sends the payment to the government, both taxed parties (domestic buyers and foreign sellers) will absorb some of the costs of the tariff, while domestic sellers will benefit from the protectionism provided by tariffs and be able to sell at a higher price per unit.
Marginal benefit
All of the numbers discussed below are part of a helper Google Sheet I put together for this analysis. Also, apologies about the jagged lines in the charts below, I hadn’t realized before starting on this that there are some difficulties with creating supply and demand charts in Google Sheets.
Let’s say I absolutely love apples, they’re my favorite food. How much would I be willing to pay for a single apple? You might say “$1, that’s the price in the supermarket,” and in many ways you’d be right. If I walk into supermarket A, see apples on sale for $50, and know that I can buy them at supermarket B for $1, I’ll almost certainly leave A and go buy at B.
But that’s not what I mean. What I mean is: how high would the price of apples have to go everywhere so that I’d no longer be willing to buy a single apple? This is a purely personal, subjective opinion. It’s impacted by how much money I have available, other expenses I need to cover, and how much I like apples. But let’s say the number is $5.
How much would I be willing to pay for another apple? Maybe another $5. But how much am I willing to pay for the 1,000th apple? 10,000th? At some point, I’ll get sick of apples, or run out of space to keep the apples, or not be able to eat, cook, and otherwise preserve all those apples before they rot.
The point being: I’ll be progressively willing to spend less and less money for each apple. This form of analysis is called marginal benefit: how much benefit (expressed as dollars I’m willing to spend) will I receive from each apple? This is a downward sloping function: for each additional apple I buy (quantity demanded), the price I’m willing to pay goes down. This is what gives my personal demand curve. And if we aggregate demand curves across all market participants (meaning: everyone interested in buying apples), we end up with something like this:
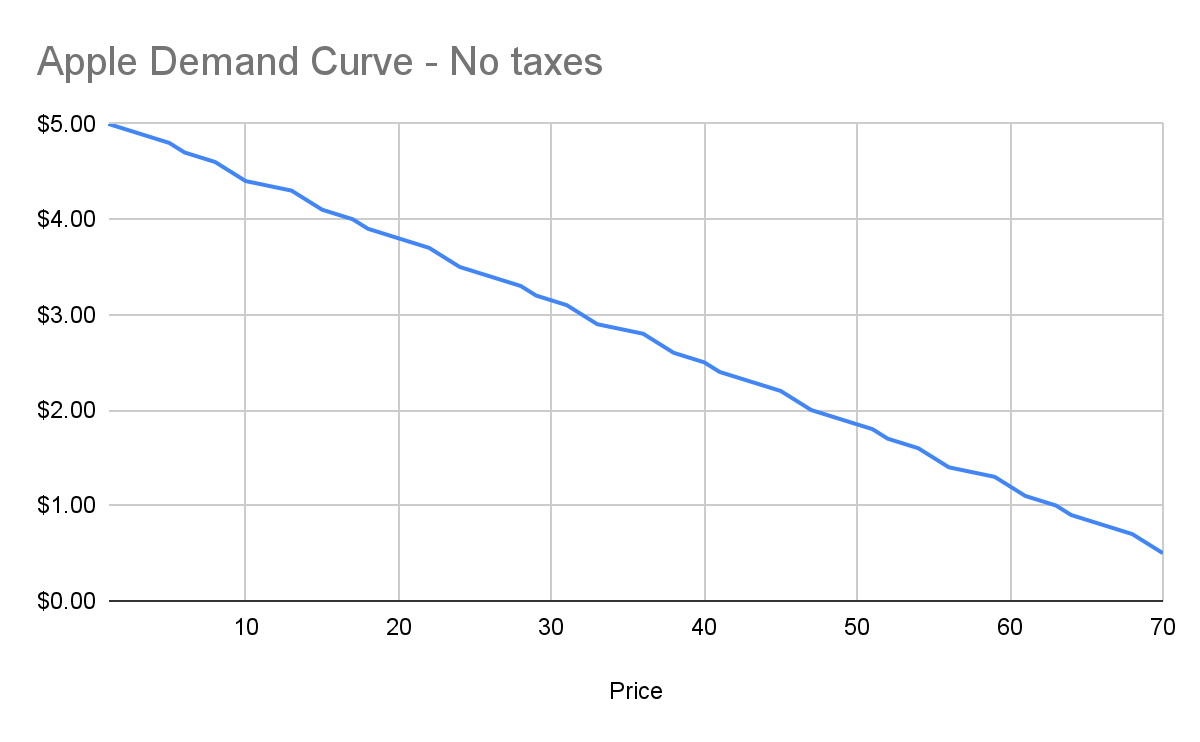
Assuming no changes in people’s behavior and other conditions in the market, this chart tells us how many apples will be purchased by our buyers at each price point between $0.50 and $5. And ceteris paribus (all else being equal), this will continue to be the demand curve for apples.
Marginal cost
Demand is half the story of economics. The other half is supply, or: how many apples will I sell at each price point? Supply curves are upward sloping: the higher the price, the more a person or company is willing and able to sell a product.
Let’s understand why. Suppose I have an apple orchard. It’s a large property right next to my house. With about 2 minutes of effort, I can walk out of my house, find the nearest tree, pick 5 apples off the tree, and call it a day. 5 apples for 2 minutes of effort is pretty good, right?
Yes, there was all the effort necessary to buy the land, and plant the trees, and water them… and a bunch more than I likely can’t even guess at. We’re going to ignore all of that for our analysis, because for short-term supply-and-demand movement, we can ignore these kinds of sunk costs. One other simplification: in reality, supply curves often start descending before ascending. This accounts for achieving efficiencies of scale after the first number of units purchased. But since both these topics are unneeded for understanding taxes, I won’t go any further.
Anyway, back to my apple orchard. If someone offers me $0.50 per apple, I can do 2 minutes of effort and get $2.50 in revenue, which equates to a $75/hour wage for me. I’m more than happy to pick apples at that price!
However, let’s say someone comes to buy 10,000 apples from me instead. I no longer just walk out to my nearest tree. I’m going to need to get in my truck, drive around, spend the day in the sun, pay for gas, take a day off of my day job (let’s say it pays me $70/hour). The costs go up significantly. Let’s say it takes 5 days to harvest all those apples myself, it costs me $100 in fuel and other expenses, and I lose out on my $70/hour job for 5 days. We end up with:
- Total expenditure: $100 + $70 * 8 hours a day * 5 days \== $2900
- Total revenue: $5000 (10,000 apples at $0.50 each)
- Total profit: $2100
So I’m still willing to sell the apples at this price, but it’s not as attractive as before. And as the number of apples purchased goes up, my costs keep increasing. I’ll need to spend more money on fuel to travel more of my property. At some point I won’t be able to do the work myself anymore, so I’ll need to pay others to work on the farm, and they’ll be slower at picking apples than me (less familiar with the property, less direct motivation, etc.). The point being: at some point, the number of apples can go high enough that the $0.50 price point no longer makes me any money.
This kind of analysis is called marginal cost. It refers to the additional amount of expenditure a seller has to spend in order to produce each additional unit of the good. Marginal costs go up as quantity sold goes up. And like demand curves, if you aggregate this data across all sellers, you get a supply curve like this:
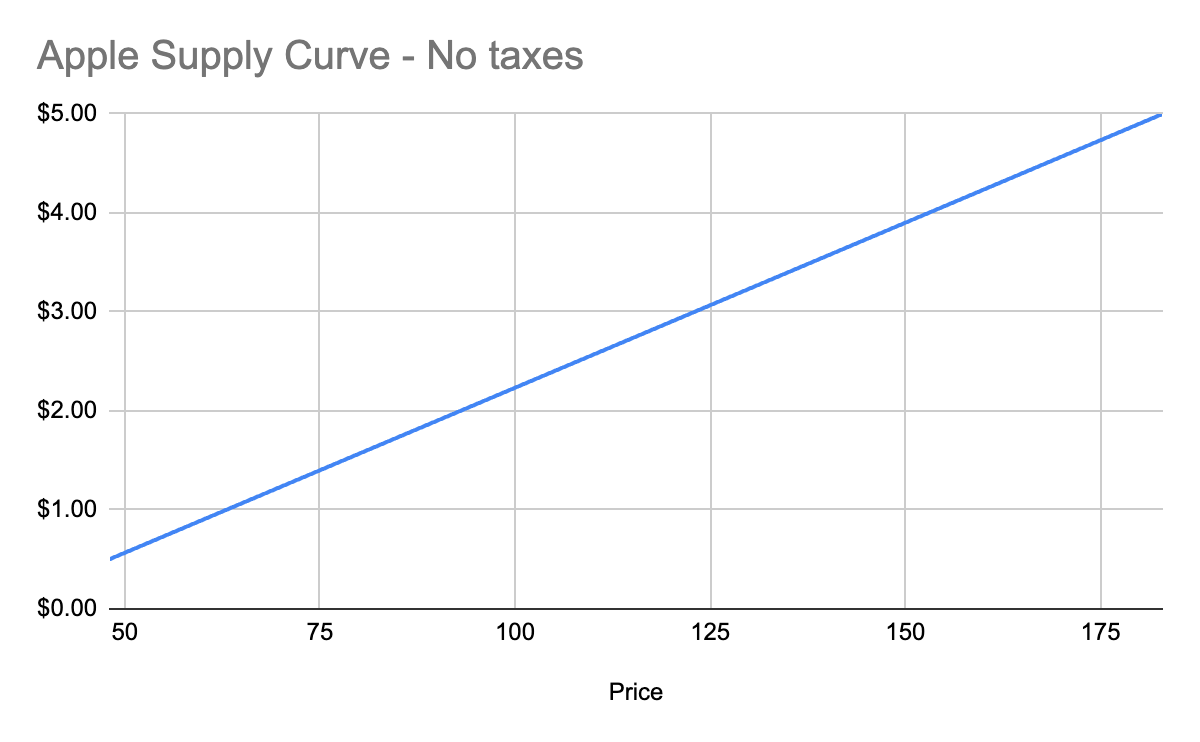
Equilibrium price
We now know, for every price point, how many apples buyers will purchase, and how many apples sellers will sell. Now we find the equilibrium: where the supply and demand curves meet. This point represents where the marginal benefit a buyer would receive from the next buyer would be less than the cost it would take the next seller to make it. Let’s see it in a chart:
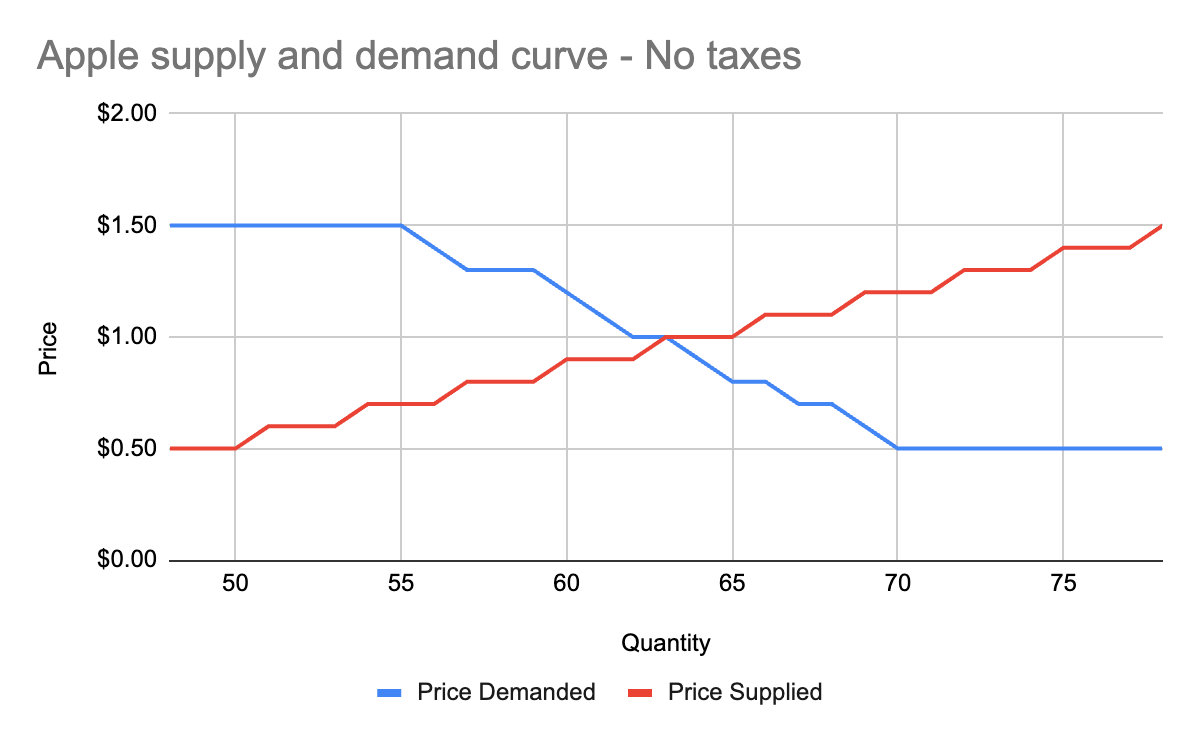
You’ll notice that these two graphs cross at the $1 price point, where 63 apples are both demanded (bought by consumers) and supplied (sold by producers). This is our equilibrium price. We also have a visualization of the surplus created by these trades. Everything to the left of the equilibrium point and between the supply and demand curves represents surplus: an area where someone is receiving something of more value than they give. For example:
- When I bought my first apple for $1, but I was willing to spend $5, I made $4 of consumer surplus. The consumer portion of the surplus is everything to the left of the equilibrium point, between the supply and demand curves, and above the equilibrium price point.
- When a seller sells his first apple for $1, but it only cost $0.50 to produce it, the seller made $0.50 of producer surplus. The producer portion of the surplus is everything to the left of the equilibrium point, between the supply and demand curves, and below the equilibrium price point.
Another way of thinking of surplus is “every time someone got a better price than they would have been willing to take.”
OK, with this in place, we now have enough information to figure out how to price in the tariff, which we’ll treat as a negative externality.
Modeling taxes
Alright, the government has now instituted a $0.50 tariff on every apple sold within the US by a foreign producer. We can generally model taxes by either increasing the marginal cost of each unit sold (shifting the supply curve up), or by decreasing the marginal benefit of each unit bought (shifting the demand curve down). In this case, since only some of the producers will pay the tax, it makes more sense to modify the supply curve.
First, let’s see what happens to the foreign seller-only supply curve when you add in the tariff:
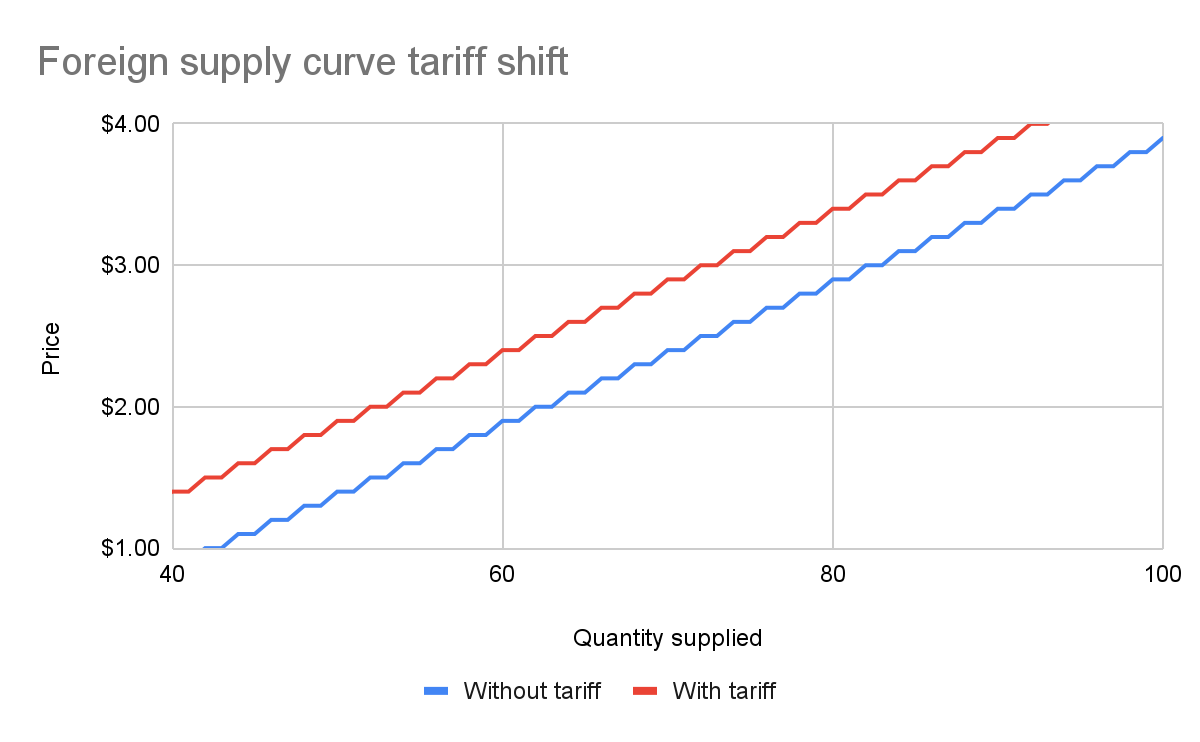
With the tariff in place, for each quantity level, the price at which the seller will sell is $0.50 higher than before the tariff. That makes sense: if I was previously willing to sell my 82nd apple for $3, I would now need to charge $3.50 for that apple to cover the cost of the tariff. We see this as the tariff “pushing up” or “pushing left” the original supply curve.
We can add this new supply curve to our existing (unchanged) supply curve for domestic-only sellers, and we end up with a result like this:
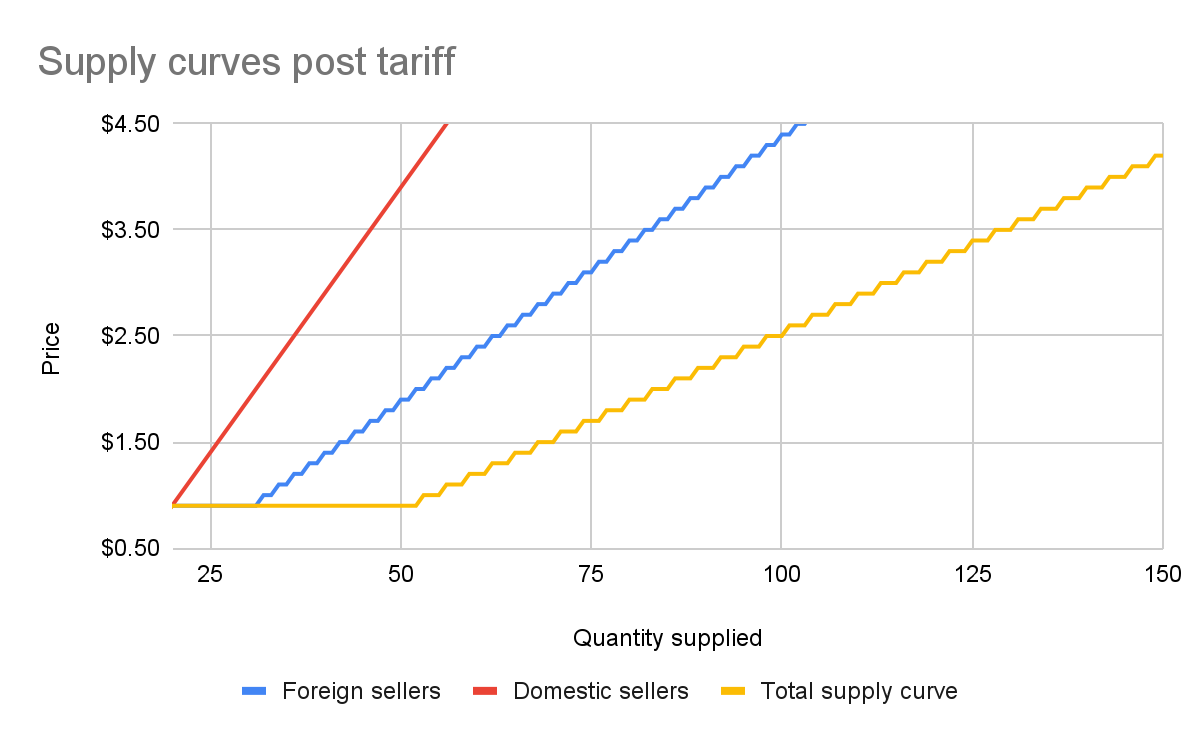
The total supply curve adds up the individual foreign and domestic supply curves. At each price point, we add up the total quantity each group would be willing to sell to determine the total quantity supplied for each price point. Once we have that cumulative supply curve defined, we can produce an updated supply-and-demand chart including the tariff:
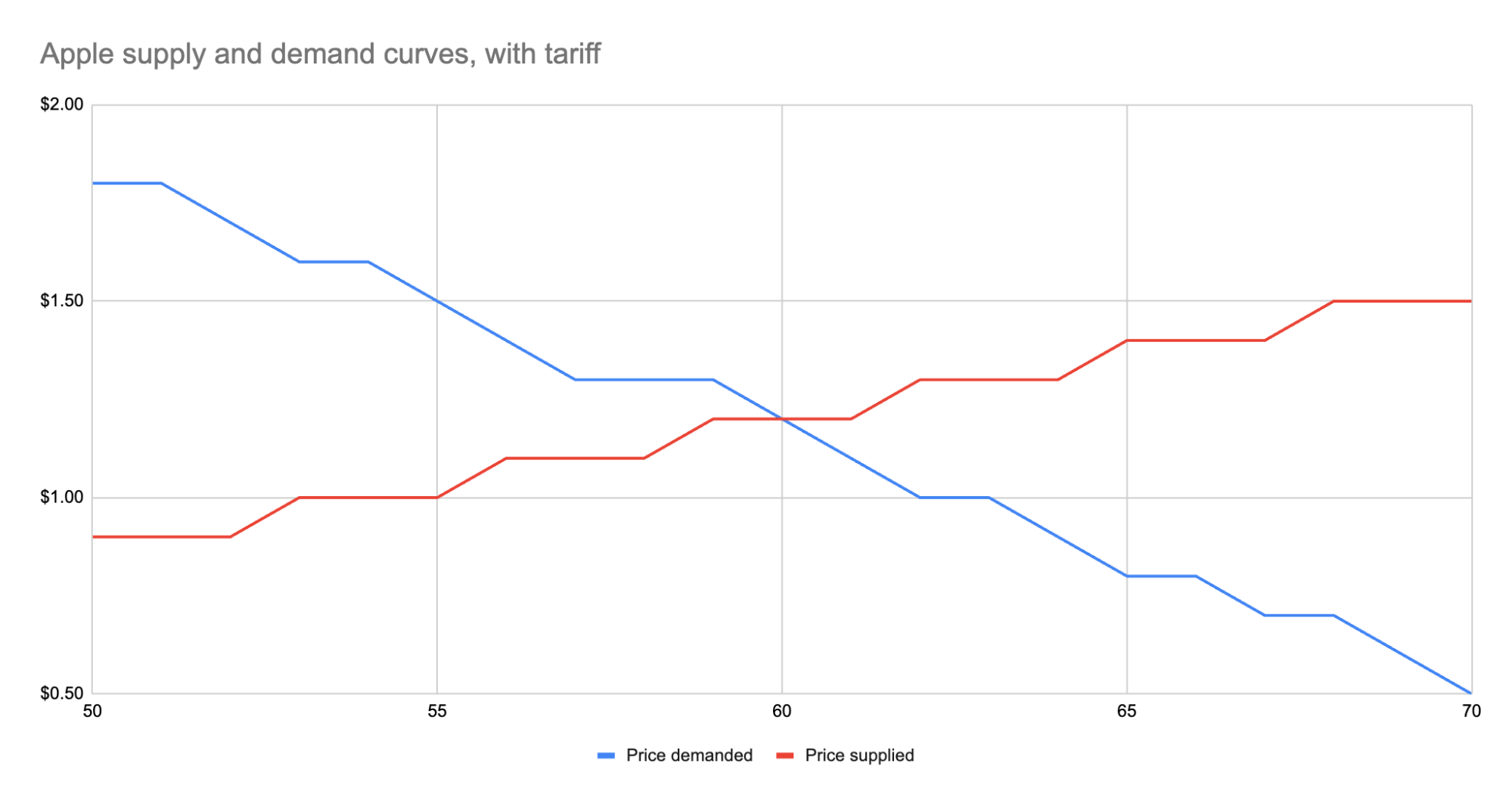
As we can see, the equilibrium has shifted:
- The equilibrium price paid by consumers has risen from $1 to $1.20.
- The total number of apples purchased has dropped from 63 apples to 60 apples.
- Consumers therefore received 3 less apples. They spent $72 for these 60 apples, whereas previously they spent $63 for 3 more apples, a definite decrease in consumer surplus.
- Foreign producers sold 36 of those apples (see the raw data in the linked Google Sheet), for a gross revenue of $43.20. However, they also need to pay the tariff to the US government, which accounts for $18, meaning they only receive $25.20 post-tariff. Previously, they sold 42 apples at $1 each with no tariff to be paid, meaning they took home $42.
- Domestic producers sold the remaining 24 apples at $1.20, giving them a revenue of $28.80. Since they don’t pay the tariff, they take home all of that money. By contrast, previously, they sold 21 apples at $1, for a take-home of $21.
- The government receives $0.50 for each of the 60 apples sold, or in other words receives $30 in revenue it wouldn’t have received otherwise.
We could be more specific about the surpluses, and calculate the actual areas for consumer surplus, producer surplus, inefficiency from the tariff, and government revenue from the tariff. But I won’t bother, as those calculations get slightly more involved. Instead, let’s just look at the aggregate outcomes:
- Consumers were unquestionably hurt. Their price paid went up by $0.20 per apple, and received less apples.
- Foreign producers were also hurt. Their price received went down from the original $1 to the new post-tariff price of $1.20, minus the $0.50 tariff. In other words: foreign producers only receive $0.70 per apple now. This hurt can be mitigated by shifting sales to other countries without a tariff, but the pain will exist regardless.
- Domestic producers scored. They can sell less apples and make more revenue doing it.
- And the government walked away with an extra $30.
Hopefully you now see the answer to the original questions. Importantly, while the government imposed a $0.50 tariff, neither side fully absorbed that cost. Consumers paid a bit more, foreign producers received a bit less. The exact details of how that tariff was split across the groups is mediated by the relevant supply and demand curves of each group. If you want to learn more about this, the relevant search term is “price elasticity,” or how much a group’s quantity supplied or demanded will change based on changes in the price.
Other taxes
Most taxes are some kind of a tax on trade. Tariffs on apples is an obvious one. But the same applies to income tax (taxing the worker for the trade of labor for money) or payroll tax (same thing, just taxing the employer instead). Interestingly, you can use the same model for analyzing things like tax incentives. For example, if the government decided to subsidize domestic apple production by giving the domestic producers a $0.50 bonus for each apple they sell, we would end up with a similar kind of analysis, except instead of the foreign supply curve shifting up, we’d see the domestic supply curve shifting down.
And generally speaking, this is what you’ll always see with government involvement in the economy. It will result in disrupting an existing equilibrium, letting the market readjust to a new equilibrium, and incentivization of some behavior, causing some people to benefit and others to lose out. We saw with the apple tariff, domestic producers and the government benefited while others lost.
You can see the reverse though with tax incentives. If I give a tax incentive of providing a deduction (not paying income tax) for preschool, we would end up with:
- Government needs to make up the difference in tax revenue, either by raising taxes on others or printing more money (leading to inflation). Either way, those paying the tax or those holding government debased currency will pay a price.
- Those people who don’t use the preschool deduction will receive no benefit, so they simply pay a cost.
- Those who do use the preschool deduction will end up paying less on tax+preschool than they would have otherwise.
This analysis is fully amoral. It’s not saying whether providing subsidized preschool is a good thing or not, it simply tells you where the costs will be felt, and points out that such government interference in free economic choice does result in inefficiencies in the system. Once you have that knowledge, you’re more well educated on making a decision about whether the costs of government intervention are worth the benefits.
-
 @ 866e0139:6a9334e5
2025-03-24 10:48:58
@ 866e0139:6a9334e5
2025-03-24 10:48:58Autor: Tom-Oliver Regenauer
Grafik: Tina Ovalle.
Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier.
»Krieg ist Frieden«. Dieses zwischenzeitlich fast abgedroschen wirkende, weil in den letzten Jahren zu häufig verwendete Zitat aus George Orwells Klassiker »1984«, beschreibt zunehmend genau, was europäische Spitzenpolitiker dieser Tage als »Wehrtüchtigkeit« vermarkten – die wahnwitzige Illusion, dass Kriegswaffen der Friedenssicherung dienen.
So aber funktioniert das Geschäft industrialisierten Tötens nicht. Denn Krieg entsteht nicht organisch. Schon gar kein Weltkrieg. Militärische Konflikte globalen Ausmaßes sind stets trauriger Kulminationspunkt langjähriger Entwicklungen. Sie beginnen mit Partikularinteressen, diplomatischen Kontakten, bilateralen Absprachen, militärisch-industriellen Konjunkturprogrammen und der Etablierung von Verteidigungsbündnissen. Kriege sind von langer Hand geplante Disruptionen, die genutzt werden, um Paradigmenwechsel zu rechtfertigen – Entwicklungen, die der Bevölkerung ohne eine solch existenzielle Bedrohung nicht unterzujubeln sind. So gäbe es ohne die beiden ersten Weltkriege heute weder die Bank für Internationalen Zahlungsausgleich noch die Vereinten Nationen oder die NATO. Und auch das herrschende, auf Verschuldung basierende und von Zentralbankkartellen dominierte Weltfinanzsystem, das darauf ausgelegt ist, Staaten und damit deren Bevölkerung schleichend zu enteignen, wäre so nicht entstanden – siehe Bretton Woods und »Nixon Schock«.
Wem dienen Kriege?
Folgt man der tatsächlichen Geschichte des Ersten Weltkrieges, die nicht 1914 mit der Ermordung von Erzherzog Franz Ferdinand, sondern bereits 1891 in Südafrika begann – siehe Teil 1 und 2 meines diesbezüglichen Essays – wird rasch deutlich, wem Kriege dienen. Und damit auch, von wem sie ausgelöst werden: Von Finanzkartellen, die zunächst an der Aufrüstung, dann an der Finanzierung des Krieges und zum Schluss am Wiederaufbau verdienen – ganz zu schweigen von der supranationalen Konsolidierung und Zentralisierung von Finanzmacht, die mit derartigen geopolitischen Verwerfungen einhergeht.
Im Falle der beiden Weltkriege sind diese Hintergründe gut belegt und detailliert nachvollziehbar. Man muss sie nur lesen. Weil Geschichte, zumindest die offiziell goutierte und gelehrte Variante, aber bedauerlicherweise von den Gewinnern geschrieben wird, sind wir scheinbar dazu verdammt, sie zu wiederholen. Dem geschichtsaffinen Leser dürfte es derweil nicht allzu schwer fallen, Parallelen zwischen der Zeit vor den beiden Weltkriegen und der Gegenwart auszumachen.
DIE FRIEDENSTAUBE JETZT ABONNIEREN:
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel in Ihr Postfach, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht).
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):
Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: milosz@pareto.space oder kontakt@idw-europe.org.
Zum einen stimmt Trump die USA auf Isolationismus ein. Zum anderen lässt er das US-Militär gleichzeitig Öl in die bestehenden Brandherde in Europa, Nahost und dem Indopazifik gießen. Gleichzeitig läuten seine Strafzölle eine Phase internationaler Handelskriege ein, die den Rest der Welt zur Reaktion zwingt. Nicht umsonst spricht Ursula von der Leyen nun von »ReARM Europe« und will bis zu 800 Milliarden Euro für »Wiederaufrüstung« mobilisieren. Nicht von ungefähr wirft Friedrich Merz, ehemaliger BlackRock-Manager, auf dem Weg ins Kanzleramt mit »Sondervermögen« um sich und möchte 500 Milliarden in die Bundeswehr investieren. Vielleicht hat ihn Larry Fink oder die Teilnahme an der Bilderberg Konferenz 2024 in Madrid inspiriert – standen dort doch unter anderem die »Zukunft der Kriegsführung« und die »geopolitische Landschaft« auf der Agenda.
Es besteht kein Zweifel: Wir befinden uns in einer Vorkriegszeit. Die Frage ist nur, wie dieser Krieg aussehen wird und wann er beginnt. Denn die moderne Informationskriegsführung gegen die breite Bevölkerung läuft spätestens seit 9/11 auf Hochtouren – und intensivierte sich nach der Markeinführung des Smartphones im Jahr 2007 konstant. Es hat Gründe, warum ich einen Großteil meiner Artgenossen heute als Smombie bezeichne.
Zeit, für den Frieden zu kämpfen
Wie jedoch ein kinetischer Krieg in den 2020er Jahren aussehen wird, vor allem, wenn atomar bewaffnete, mit Drohnen, Robotern und KI ausgestattete Supermächte sich gegenüberstehen, weiß niemand. Den Ersten Weltkrieg konnte man sich damals auch nicht vorstellen – denn bis zu diesem Zeitpunkt gab es keine derartig weitreichenden »Verteidigungsallianzen« und »Bündnisfälle«. Auch die Waffen, die im Zweiten Weltkrieg zum Einsatz kommen sollten, waren neu. Das Ausmaß der Zerstörung eine todbringende Zäsur.
Wenig verwunderlich also, dass die Reprise dieser zivilisatorischen Katastrophe knapp 60 Millionen mehr Menschen das Leben kostete als die Premiere – und den perfekten Hebel zur Etablierung der postmodernen »Global Governance« bot. Einem inhumanen, antidemokratischen, zusehends totalitären Herrschaftskonstrukt, das sich nun mit der aus dem Elfenbeinturm kommunizierten »Zeitenwende«, »Wehrtüchtigkeit« und »ReARM Europe« anschickt, uns in einen Dritten Weltkrieg zu manövrieren.
Es ist Zeit, nein zu sagen. Nein zu Sondervermögen. Nein zu Aufrüstung. Nein zu Massenvernichtungswaffen. Und nein zu Konflikten, die stets von jenen angezettelt werden, die darin »nicht sterben« werden, wie Robert Habeck im Februar 2022 bei Maischberger selbst einräumte. Nein zu Krieg!
Wer seine Kinder nicht an die Front schicken oder am eigenen Leib erfahren möchte, welche automatisiert mordenden Waffengattungen in einem Dritten Weltkrieg zum Einsatz kommen, sollte für den Frieden kämpfen. Mit allen Mitteln – gemeinsam – und zwar jetzt. Bedarf es für die finale Ausgestaltung der »vierten industriellen Revolution«, für Agenda 2030, C40-Städte und Net Zero 2050, sprich, dem digitalen Gulag von morgen, einer globalen militärischen Disruption – und das scheint im Lichte der Vergangenheit durchaus wahrscheinlich – bleibt uns nicht mehr allzu viel Zeit, um Sand ins Getriebe der aufheulenden Kriegsmaschinerie zu streuen.
Tom-Oliver Regenauer, Jahrgang 1978, war nach betriebswirtschaftlicher Ausbildung in verschiedenen Branchen und Rollen tätig, unter anderem als Betriebsleiter, Unternehmens- und Management-Berater sowie internationaler Projektmanager mit Einsätzen in über 20 Ländern. Seit Mitte der 90er-Jahre ist er zudem als Musikproduzent und Texter aktiv und betreibt ein unabhängiges Plattenlabel. Der in Deutschland geborene Autor lebt seit 2009 in der Schweiz. Zuletzt erschienen von ihm „Homo Demens — Texte zu Zeitenwende, Technokratie und Korporatismus“ (2023), „Truman Show“ (2024) und "HOPIUM" (2025). Weitere Informationen unter www.regenauer.press.\ HOPIUM jetzt direkt im Shop oder im Handel.
Wir testen derzeit den Mailversand an allen Artikeln. In Zukunft bekommen Sie ca. drei Mailsendungen der Friedenstaube pro Woche.
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren, zappen etc.)? Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ fd208ee8:0fd927c1
2025-02-02 10:33:19
@ fd208ee8:0fd927c1
2025-02-02 10:33:19GitCitadel Development Operations
We, at GitCitadel, have been updating, moving, and rearranging our servers, for quite some time. As a rather large, complex, sprawling project, we have the infrastructure setup to match, so we've decided to give you all a quick run-down of what we are doing behind-the-scenes.
Supplier Coordination
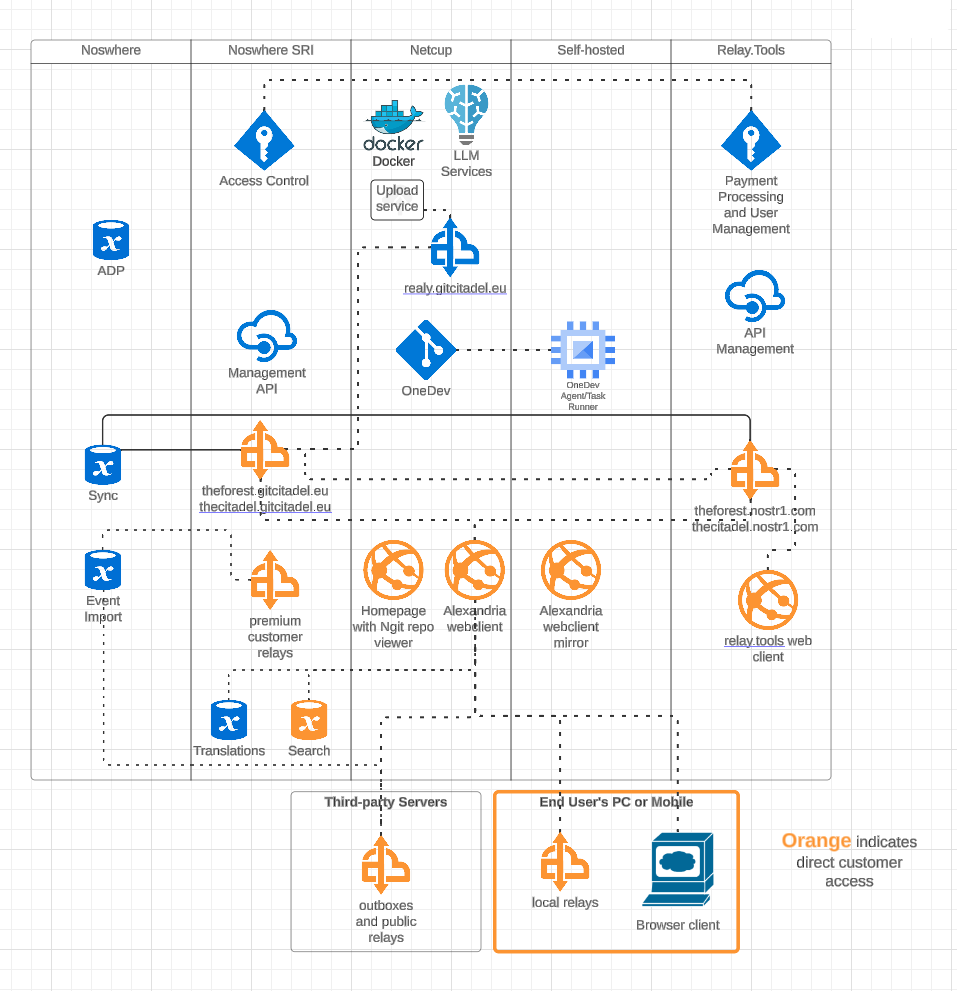
Our first task, this week, was figuring out who would host what where. We have four different locations, where our infra is stored and managed, including two locations from our suppliers. We got that straightened out, quickly, and it's all slowly coming together and being connected and networked. Exciting to watch our DevOps landscape evolve and all of the knowledge-transfer that the interactions provide.
OneDev Implementation
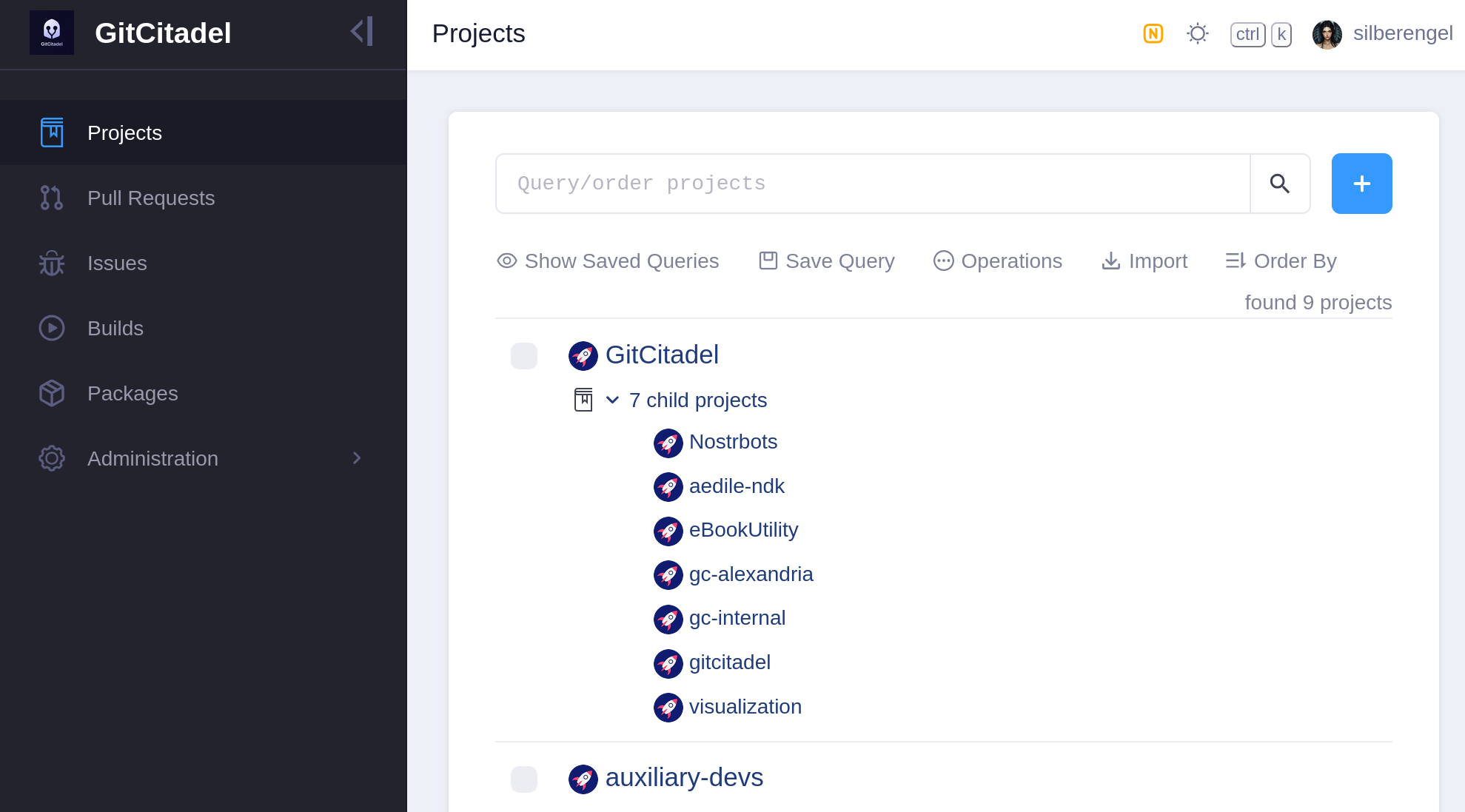
Our biggest internal infra project this week was the migration of all of our issues from Jira, build scripts from Jenkins, and repos from GitHub to a self-hosted OneDev instance. In the future, all of our internal build, test, issue, patch/PR, etc. effort will take place there. We also have a separate repo there for communicating with external developers and suppliers.
Our team's GitHub projects will be demoted to mirrors and a place for external devs to PR to. Public issues and patches will continue to be managed over our self-hosted GitWorkshop instance.
We're especially glad to finally escape the GitHub Gulag, and avoid being bled dry by Jira fees, without having to give up the important features that we've come to know and love. So, yay!
Next Infrasteps
Automated Testing
Now, that we have everything tied up in one, neat, backed-up package, we can finally move on to the nitty-gritty and the dirty work. So, we're rolling up our sleeves and writing the Selenium smoke test for our Alexandria client. We'll be running that in Docker containers containing different "typical Nostr" images, such as Chrome browser with Nostr Connect signing extension, or Firefox browser with Nos2x-fox extension. Once we get the Nsec Bunker and Amber logins going, we'll add test cases and images for them, as well. (Yes, we can do Bunker. I hope you are in awe at our powers).
We are also designing an automated infrastructure test, that will simply rattle through all the various internal and external websites and relays, to make sure that everything is still online and responsive.
After that, a Gherkin-based Behave feature test for Alexandria is planned, so that we can prevent regression of completed functionality, from one release to the next.
The Gherkin scenarios are written and attached to our stories before development begins (we use acceptance tests as requirements), a manual test-execution is then completed, in order to set the story to Done. These completed scenarios will be automated, following each release, with the resulting script linked to from the origin story.
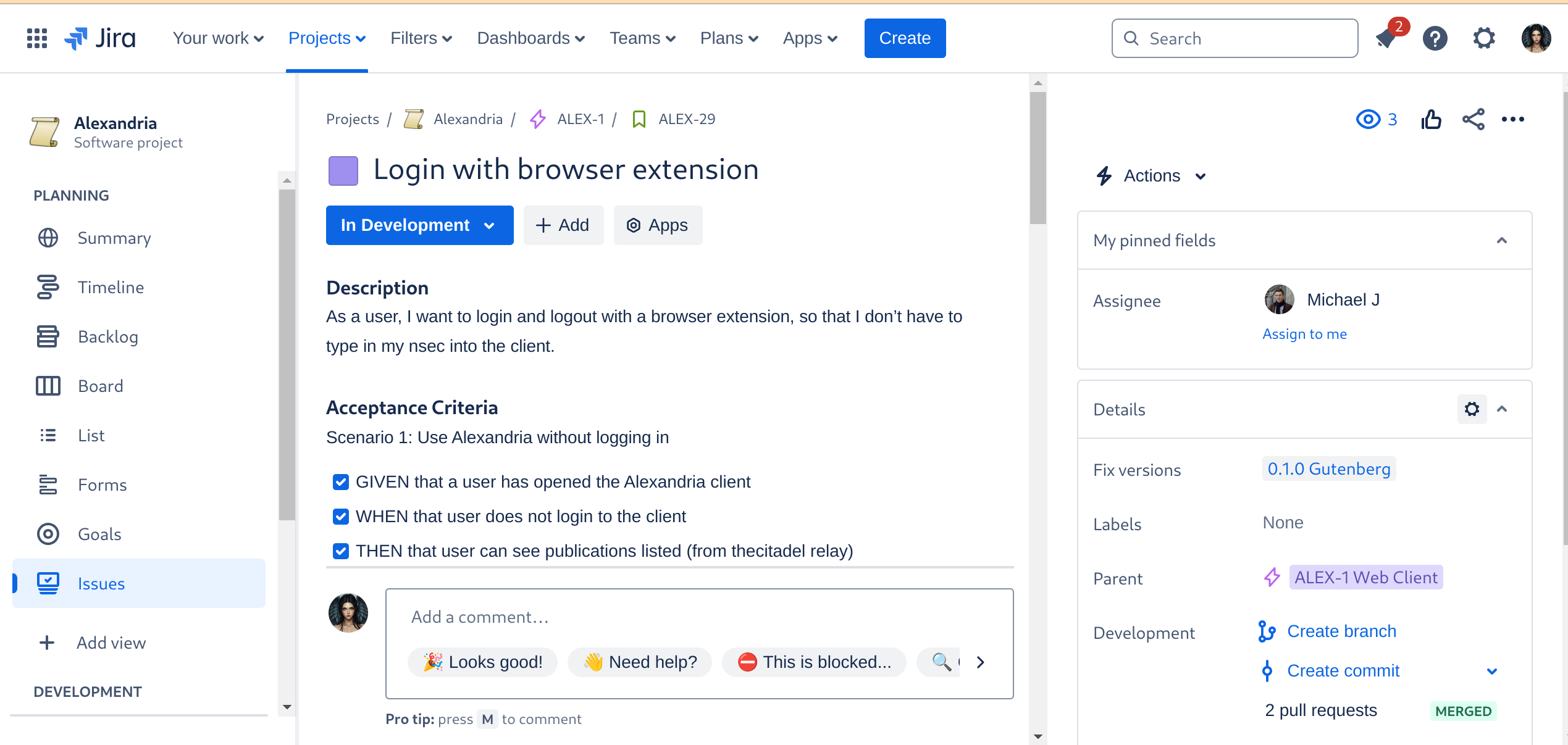
Automated Builds
As the crowning glory of every DevOps tool chain stands the build automation. This is where everything gets tied together, straightened out, configured, tested, measured, and -- if everything passes the quality gates -- released. I don't have to tell you how much time developers spend staring at the build process display, praying that it all goes through and they can celebrate a Green Wave.
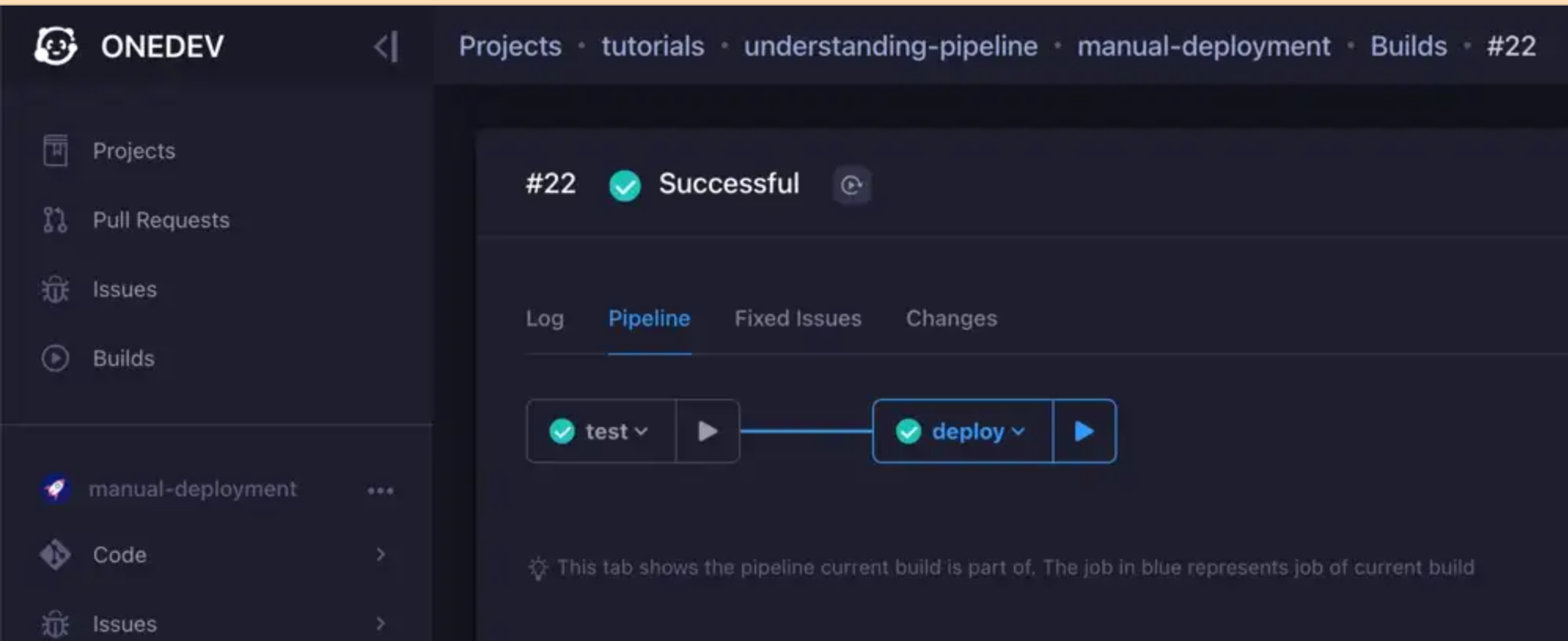
We are currently designing the various builds, but the ones we have defined for the Alexandria client will be a continuous delivery pipeline, like so:
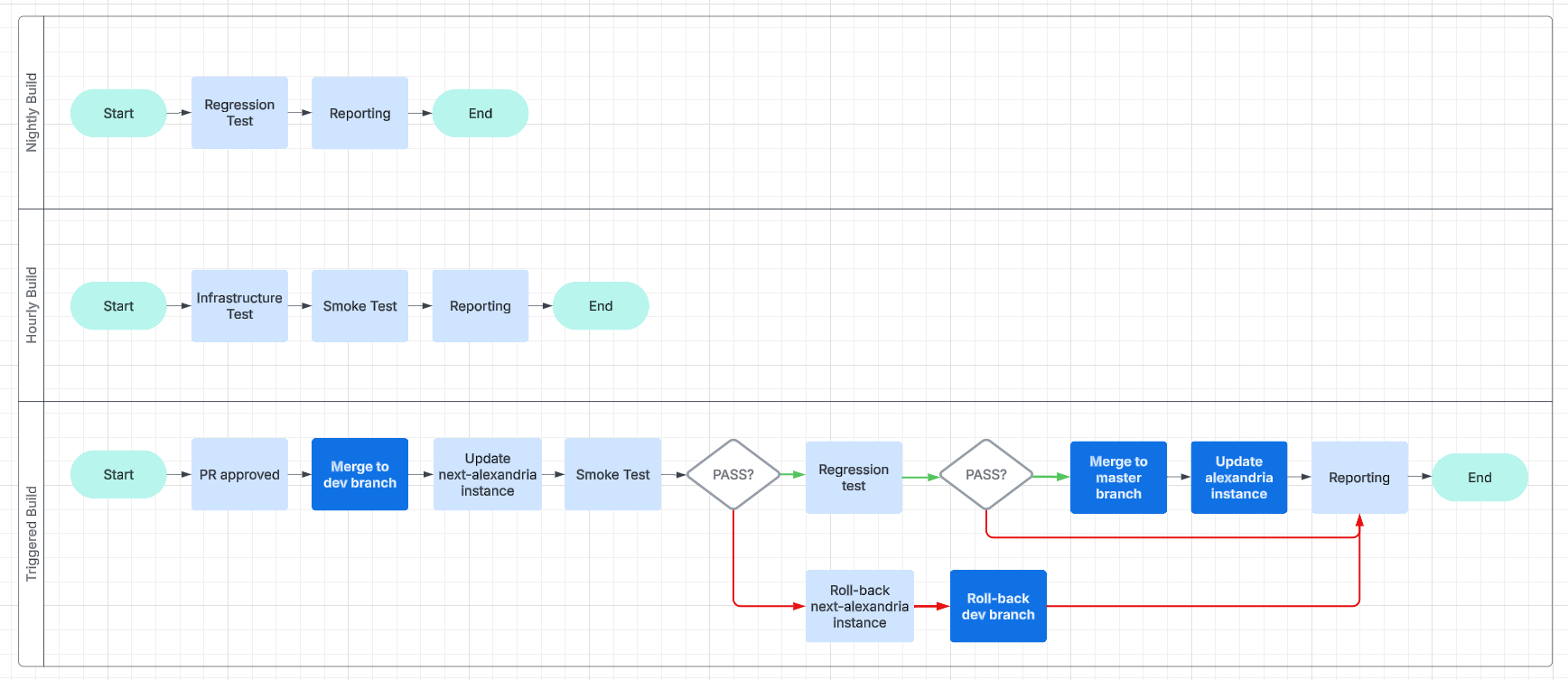
This will make it easier for us to work and collaborate asynchronously and without unnecessary delays.
Expanding the Status Page
And, finally, we get to the point of all of this busyness: reporting.
We are going to have beautiful reports, and we are going to post them online, on our status page. We will use bots, to inform Nostriches of the current status of our systems, so go ahead and follow our GitCitadel DevOps npub, to make sure you don't miss out on the IT action.
Building on stone
All in all, we're really happy with the way things are humming along, now, and the steady increase in our productivity, as all the foundational work we've put in starts to pay off. It's getting easier and easier to add new team members, repos, or features/fixes, so we should be able to scale up and out from here. Our GitCitadel is built on a firm foundation.
Happy building!
-
 @ 9e69e420:d12360c2
2025-02-01 11:16:04
@ 9e69e420:d12360c2
2025-02-01 11:16:04Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.

CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language.
One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse.
-
 @ d560dbc2:bbd59238
2025-03-24 10:18:44
@ d560dbc2:bbd59238
2025-03-24 10:18:44When it comes to task management, most of us are familiar with the traditional approach: plan your day, set deadlines, and create detailed schedules to stay on top of everything. But what if there’s a better way—a method that doesn’t require meticulous planning, yet ensures you’re always working on the right task at the right time?
Enter the 2-5 Rule, an “anti-planning” concept that focuses on which task to act on right now, rather than creating a rigid plan for the future. In this deep dive, we’ll explore what makes the 2-5 Rule stand out, how it works, why it’s so effective, and how TaskforUs brings this innovative approach to life. Whether you’re renewing a passport or keeping in touch with a loved one, the 2-5 Rule offers a refreshingly simple way to manage your tasks without the stress of planning.
What Is the 2-5 Rule?
The 2-5 Rule is a task management method that prioritizes tasks based on their timing—not a detailed schedule. Instead of planning exactly when to do each task, you simply:
- Enter the task into a system like TaskforUs.
- Assign it a time unit (days, weeks, months, or years).
- Let the algorithm decide when it should climb to the top of your priority list.
The “2-5” refers to the ideal action window: you should act on a task within 2 to 5 of its assigned time units. For example:
- Daily tasks: (e.g., “Do cardio”) should be done every 2-5 days.
- Weekly tasks: (e.g., “Schedule dinner with a friend”) should be acted on every 2-5 weeks.
- Monthly tasks: (e.g., “Review budget”) have a window of 2-5 months.
- Yearly tasks: (e.g., “Reassess career goals”) should be revisited every 2-5 years.
This sweet spot ensures tasks are neither rushed nor neglected.
Key Point: The 2-5 Rule isn’t about planning—it’s about capturing tasks and letting the system determine their priority based on timing. Simply enter the task, set its time unit, and provide either the last date you acted on it or a fixed due date (using Fix Mode for specific events). The system does the rest.
How It Works: No Planning Required
When you add a task to TaskforUs, you assign it a time unit based on how often you want to act on it:
- Daily tasks: Act every 2-5 days (e.g., “Do cardio”).
- Weekly tasks: Act every 2-5 weeks (e.g., “Meet a friend for dinner”).
- Monthly tasks: Act every 2-5 months (e.g., “Review budget”).
- Yearly tasks: Act every 2-5 years (e.g., “Renew passport”).
For recurring tasks, you enter the last date you acted on them (the “last act date”). For date-specific tasks, you can use Fix Mode to set a due date. The 2-5 Rule calculates the task’s priority based on how much time has passed since the last action or how close the due date is—ensuring it rises to the top at just the right moment.
Real-Life Examples of the 2-5 Rule in Action
Example 1: Renewing Your Passport
-
Scenario:
You get your passport today and know it needs to be renewed every 5 years. You don’t want to plan the renewal far in advance—you just want a reminder at the right time. -
Implementation:
- Add the task “Renew passport” and set its time unit to yearly.
-
Enter the “last act date” as today’s date (e.g., March 24, 2025) or use Fix Mode to set the exact expiration date (e.g., March 24, 2030).
-
Outcome:
The task starts low on your priority list. As time passes, it climbs based on the 2-5 Rule. After 2 years, it begins to rise; by 5 years, it’s nearing the top—ensuring you act before the passport expires.
Example 2: Meeting Uncle Lars Regularly
-
Scenario:
You want to meet your Uncle Lars regularly but not too often. You’d like to see him about 10 times a year (roughly once every 5 weeks). However, to give yourself more flexibility, you choose a longer time unit. -
Implementation:
- Add the task “Meet/eat with Uncle Lars” and set its time unit to monthly.
-
Set the “last act date” as the most recent time you met him (e.g., March 1, 2025).
-
Outcome:
Over time, the task slowly climbs in your priority list. After 2 months, it starts gaining focus; by 5 months, it becomes urgent—nudge you to reach out and schedule a meeting, all without needing to plan the exact date in advance.
The Origins of the 2-5 Rule: An Anti-Planning Revolution
The 2-5 Rule isn’t entirely new—it has roots in productivity and behavioral science, emerging as a response to the complexity of traditional task management systems that require detailed schedules, deadlines, and constant reviews. Influential figures, including Bill Gates, have reportedly praised its simplicity for managing tasks without over-planning.
- Why It Works:
The 2-5 Rule leverages the natural rhythm of tasks, ensuring that you act within an optimal time window without micromanaging your schedule. It aligns with our intuition—you don’t need to plan exactly when to call a friend; you just know it’s been a while, and it’s time to reconnect.
Why the 2-5 Rule Works: The Science Behind Anti-Planning
-
Reduces Decision Fatigue:
Traditional planning forces you to decide when to act on each task, which can be mentally exhausting. The 2-5 Rule automates prioritization, freeing up mental energy. -
Aligns with Natural Rhythms:
Research on habit formation shows that consistency is key. The 2-5 window ensures you act within a natural timeframe—tasks feel urgent after 2 units but are at risk of being neglected by 5 units. -
Prevents Over-Planning Stress:
Detailed plans can lead to stress when life interferes. The 2-5 Rule removes the need for rigid scheduling, letting you focus on action rather than planning. -
Ensures Critical Tasks Don’t Slip Through the Cracks:
With Fix Mode, date-specific tasks like passport renewals or birthdays climb in priority as the due date approaches, ensuring you never miss a deadline.
How TaskforUs Brings the 2-5 Rule to Life
TaskforUs is a web-based platform that makes the 2-5 Rule actionable, elevating the anti-planning concept with features designed for ease and precision:
-
Add Tasks Easily:
Enter a task, set its time unit (days, weeks, months, or years), and provide the last act date or a fixed due date for Fix Mode tasks. -
Top Task:
TaskforUs automatically highlights your most urgent task based on the 2-5 Rule—telling you exactly what to do right now. -
Focus Mode:
Display your top 3 tasks (or adjust the number) for a distraction-free view when juggling multiple priorities. -
Fix Mode:
For tasks tied to specific dates, Fix Mode ensures they rise in priority as the due date approaches, peaking on the day itself. -
Category Filtering and Archiving:
Organize your tasks into categories (e.g., Work, Personal) and archive completed tasks to keep your list clutter-free. -
Export Tasks:
Download your tasks as a CSV file for backup or analysis.
Practical Applications: More Ways to Use the 2-5 Rule
-
Health Goals:
Want to drink more water daily? Set “Drink water” as a daily task. TaskforUs will nudge you every 2-5 days to stay hydrated—no strict schedule required. -
Work Projects:
Need to follow up on a client email? Set it as a weekly task. After 2 weeks, it’ll start climbing your list, ensuring you don’t forget. -
Special Dates:
Have a wedding anniversary coming up? Use Fix Mode to set the date; TaskforUs will ensure “Plan anniversary dinner” becomes your top task on that day. -
Long-Term Goals:
Want to learn a new skill every few years? Set “Explore new skill” as a yearly task, and TaskforUs will remind you every 2-5 years.
The 2-5 Rule vs. Traditional Planning: Why Anti-Planning Wins
Traditional planning methods—such as detailed schedules or comprehensive systems like Getting Things Done (GTD)—often come with drawbacks:
-
Complexity:
Detailed planning requires significant time and effort. -
Inflexibility:
Rigid plans can crumble when unexpected events occur. -
Mental Load:
Constantly deciding when to do each task contributes to decision fatigue.
The 2-5 Rule avoids these pitfalls by letting you focus on timing. You simply enter your tasks, and TaskforUs automatically prioritizes them based on the optimal action window.
Why You Should Try the 2-5 Rule with TaskforUs
The 2-5 Rule offers a fresh perspective on task management by focusing on when to act rather than what to do. It’s particularly effective for balancing short-term habits with long-term goals. Here’s why you should give it a try:
-
No Planning Needed:
Simply add your tasks and let the system handle prioritization. -
Clarity:
Always know what to do right now without overthinking. -
Flexibility:
The 2-to-5 window provides the ideal balance between prompt action and careful timing. -
Reliability:
Fix Mode ensures you never miss critical dates. -
Be Part of the Beta:
As a beta user, your feedback can shape the future of TaskforUs.
Take Control of Your Tasks Today
The 2-5 Rule is more than a productivity hack—it’s a new way to think about task management. By focusing on timing, it ensures you’re always working on the right thing at the right time. Ready to say goodbye to over-planning and hello to effortless prioritization?
Sign up for TaskforUs at task4.us and experience the 2-5 Rule in action.
Your tasks, perfectly timed—without a plan in sight. -
 @ d560dbc2:bbd59238
2025-03-24 08:54:06
@ d560dbc2:bbd59238
2025-03-24 08:54:06Task management is a challenge we all face—whether it’s juggling work deadlines, staying in touch with friends, or remembering important dates like birthdays. With endless to-do lists and competing priorities, how do you decide what to tackle next?
Enter the 2-5 Rule, a unique approach to task management that focuses on timing tasks within a specific “sweet spot”—between 2 to 5 time units—ensuring they’re neither rushed nor neglected. In this deep dive, we’ll explore what makes the 2-5 Rule stand out, how it works, and how it compares to other popular task management techniques like the 1-3-5 Rule, Eisenhower Matrix, Getting Things Done (GTD), and the Pomodoro Technique.
What Is the 2-5 Rule?
The 2-5 Rule is a timing-based task management strategy designed to help you act on tasks at the right moment. Every task has a natural rhythm or “time unit” (days, weeks, months, or years) that dictates how often it should be addressed. The rule dictates that you should act on a task within 2 to 5 of these units. For example:
- Daily tasks (e.g., “Do cardio”) should be done every 2-5 days.
- Weekly tasks (e.g., “Schedule dinner with a friend”) should be done every 2-5 weeks.
- Monthly tasks (e.g., “Review budget”) should be done every 2-5 months.
- Yearly tasks (e.g., “Reassess career goals”) should be revisited every 2-5 years.
This “sweet spot” balances urgency and flexibility—acting too soon wastes energy, while waiting too long risks neglecting the task. The 2-5 Rule is the foundation of TaskforUs, a platform that automates this process to help you prioritize tasks with precision.
Comparing the 2-5 Rule to Other Task Management Techniques
1. The 1-3-5 Rule: Daily Structure Without Timing
- Overview:
Organizes your day into 1 big task, 3 medium tasks, and 5 small tasks. - Strengths:
- Helps set realistic daily goals and forces you to prioritize.
- Weaknesses:
- Does not account for the natural rhythm or timing of tasks over longer periods.
- Comparison:
The 1-3-5 Rule is excellent for daily planning, while the 2-5 Rule provides a broader perspective by scheduling tasks over days, weeks, months, or years. They can be combined: use 1-3-5 for daily structure and the 2-5 Rule for long-term timing.
2. Eisenhower Matrix: Urgency vs. Importance
- Overview:
Categorizes tasks into four quadrants based on urgency and importance: - Urgent and Important: Do immediately.
- Important but Not Urgent: Schedule for later.
- Urgent but Not Important: Delegate.
- Neither Urgent nor Important: Eliminate.
- Strengths:
- Excellent for decision-making and eliminating time-wasters.
- Weaknesses:
- Lacks guidance on when to act on tasks that are important but not urgent.
- Comparison:
While the Eisenhower Matrix focuses on what to do, the 2-5 Rule tells you when to do it. They can work together for a complete task management system.
3. Getting Things Done (GTD): Comprehensive but Complex
- Overview:
GTD is a system to capture and organize all your tasks using steps like capture, clarify, organize, reflect, and engage. - Strengths:
- Ensures nothing is forgotten by capturing every task.
- Weaknesses:
- Can be overwhelming and time-consuming for those who prefer simplicity.
- Comparison:
GTD provides a comprehensive framework, whereas the 2-5 Rule offers a focused strategy for timing and prioritization, reducing decision fatigue.
4. Pomodoro Technique: Focus on the Present
- Overview:
Breaks work into intervals (typically 25 minutes of focused work followed by a 5-minute break). - Strengths:
- Boosts focus and prevents burnout during work sessions.
- Weaknesses:
- Doesn’t help you decide which task to tackle or manage long-term priorities.
- Comparison:
The Pomodoro Technique helps you focus on a chosen task; the 2-5 Rule helps you decide the right task to work on at the right time. They complement each other well.
Why the 2-5 Rule Stands Out
-
Integrates Behavioral Science:
Grounded in research on habit formation and decision fatigue, the 2-5 Rule leverages our natural sense of urgency to prompt action at the optimal time. -
Balances Urgency and Flexibility:
It provides a flexible window for action, ensuring tasks are handled neither too early nor too late. -
Simplifies Decision-Making:
By automating prioritization, TaskforUs reduces the mental load, so you always know which task to focus on. -
Addresses Long-Term Timing:
Unlike the Pomodoro Technique, it considers tasks over various timeframes—daily, weekly, monthly, or yearly. -
Never Misses Critical Dates:
With Fix Mode, TaskforUs ensures that date-specific tasks (e.g., birthdays) climb to the top of your list as the date approaches.
Practical Applications of the 2-5 Rule
-
Social Connections:
Task: “Schedule dinner with Alex”
Time Unit: Weeks
Application: If it’s been 3 weeks since your last meetup, TaskforUs flags it as your top task, prompting you to reconnect. -
Health Goals:
Task: “Do cardio”
Time Unit: Days
Application: If it’s been 2 days since your last workout, the platform nudges you to exercise before reaching the 5-day mark. -
Special Dates:
Task: “Wish Alex a happy birthday”
Mode: Fix Mode
Application: TaskforUs ensures the task climbs in priority as the birthday nears, becoming the top task on the day. -
Long-Term Planning:
Task: “Reassess my career path”
Time Unit: Years
Application: If it’s been 2 years since your last career review, the system prompts you to evaluate your progress and goals.
Why You Should Try the 2-5 Rule with TaskforUs
The 2-5 Rule offers a fresh perspective on task management by focusing on timing rather than solely on task content. It is particularly effective for balancing short-term habits with long-term goals. TaskforUs brings this concept to life with features such as:
- Top Task: Automatically highlights your most urgent task within the 2-5 window.
- Focus Mode: Displays your top 3 tasks (customizable) to help you concentrate.
- Fix Mode: Prioritizes date-specific tasks as their deadlines approach.
- Category Filtering and Archiving: Keeps your task list organized and clutter-free.
If you’re tired of chaotic to-do lists, missed deadlines, or the mental load of deciding what to do next, the 2-5 Rule offers a better way.
Take Control of Your Tasks Today
The 2-5 Rule is more than a productivity hack—it’s a mindset shift. By focusing on when to act, it ensures you’re always working on the right task at the right time. Ready to give it a try?
Sign up for TaskforUs at task4.usYour tasks, perfectly timed—every time.
-
 @ 97c70a44:ad98e322
2025-01-30 17:15:37
@ 97c70a44:ad98e322
2025-01-30 17:15:37There was a slight dust up recently over a website someone runs removing a listing for an app someone built based on entirely arbitrary criteria. I'm not to going to attempt to speak for either wounded party, but I would like to share my own personal definition for what constitutes a "nostr app" in an effort to help clarify what might be an otherwise confusing and opaque purity test.
In this post, I will be committing the "no true Scotsman" fallacy, in which I start with the most liberal definition I can come up with, and gradually refine it until all that is left is the purest, gleamingest, most imaginary and unattainable nostr app imaginable. As I write this, I wonder if anything built yet will actually qualify. In any case, here we go.
It uses nostr
The lowest bar for what a "nostr app" might be is an app ("application" - i.e. software, not necessarily a native app of any kind) that has some nostr-specific code in it, but which doesn't take any advantage of what makes nostr distinctive as a protocol.
Examples might include a scraper of some kind which fulfills its charter by fetching data from relays (regardless of whether it validates or retains signatures). Another might be a regular web 2.0 app which provides an option to "log in with nostr" by requesting and storing the user's public key.
In either case, the fact that nostr is involved is entirely neutral. A scraper can scrape html, pdfs, jsonl, whatever data source - nostr relays are just another target. Likewise, a user's key in this scenario is treated merely as an opaque identifier, with no appreciation for the super powers it brings along.
In most cases, this kind of app only exists as a marketing ploy, or less cynically, because it wants to get in on the hype of being a "nostr app", without the developer quite understanding what that means, or having the budget to execute properly on the claim.
It leverages nostr
Some of you might be wondering, "isn't 'leverage' a synonym for 'use'?" And you would be right, but for one connotative difference. It's possible to "use" something improperly, but by definition leverage gives you a mechanical advantage that you wouldn't otherwise have. This is the second category of "nostr app".
This kind of app gets some benefit out of the nostr protocol and network, but in an entirely selfish fashion. The intention of this kind of app is not to augment the nostr network, but to augment its own UX by borrowing some nifty thing from the protocol without really contributing anything back.
Some examples might include:
- Using nostr signers to encrypt or sign data, and then store that data on a proprietary server.
- Using nostr relays as a kind of low-code backend, but using proprietary event payloads.
- Using nostr event kinds to represent data (why), but not leveraging the trustlessness that buys you.
An application in this category might even communicate to its users via nostr DMs - but this doesn't make it a "nostr app" any more than a website that emails you hot deals on herbal supplements is an "email app". These apps are purely parasitic on the nostr ecosystem.
In the long-term, that's not necessarily a bad thing. Email's ubiquity is self-reinforcing. But in the short term, this kind of "nostr app" can actually do damage to nostr's reputation by over-promising and under-delivering.
It complements nostr
Next up, we have apps that get some benefit out of nostr as above, but give back by providing a unique value proposition to nostr users as nostr users. This is a bit of a fine distinction, but for me this category is for apps which focus on solving problems that nostr isn't good at solving, leaving the nostr integration in a secondary or supporting role.
One example of this kind of app was Mutiny (RIP), which not only allowed users to sign in with nostr, but also pulled those users' social graphs so that users could send money to people they knew and trusted. Mutiny was doing a great job of leveraging nostr, as well as providing value to users with nostr identities - but it was still primarily a bitcoin wallet, not a "nostr app" in the purest sense.
Other examples are things like Nostr Nests and Zap.stream, whose core value proposition is streaming video or audio content. Both make great use of nostr identities, data formats, and relays, but they're primarily streaming apps. A good litmus test for things like this is: if you got rid of nostr, would it be the same product (even if inferior in certain ways)?
A similar category is infrastructure providers that benefit nostr by their existence (and may in fact be targeted explicitly at nostr users), but do things in a centralized, old-web way; for example: media hosts, DNS registrars, hosting providers, and CDNs.
To be clear here, I'm not casting aspersions (I don't even know what those are, or where to buy them). All the apps mentioned above use nostr to great effect, and are a real benefit to nostr users. But they are not True Scotsmen.
It embodies nostr
Ok, here we go. This is the crème de la crème, the top du top, the meilleur du meilleur, the bee's knees. The purest, holiest, most chaste category of nostr app out there. The apps which are, indeed, nostr indigitate.
This category of nostr app (see, no quotes this time) can be defined by the converse of the previous category. If nostr was removed from this type of application, would it be impossible to create the same product?
To tease this apart a bit, apps that leverage the technical aspects of nostr are dependent on nostr the protocol, while apps that benefit nostr exclusively via network effect are integrated into nostr the network. An app that does both things is working in symbiosis with nostr as a whole.
An app that embraces both nostr's protocol and its network becomes an organic extension of every other nostr app out there, multiplying both its competitive moat and its contribution to the ecosystem:
- In contrast to apps that only borrow from nostr on the technical level but continue to operate in their own silos, an application integrated into the nostr network comes pre-packaged with existing users, and is able to provide more value to those users because of other nostr products. On nostr, it's a good thing to advertise your competitors.
- In contrast to apps that only market themselves to nostr users without building out a deep integration on the protocol level, a deeply integrated app becomes an asset to every other nostr app by becoming an organic extension of them through interoperability. This results in increased traffic to the app as other developers and users refer people to it instead of solving their problem on their own. This is the "micro-apps" utopia we've all been waiting for.
Credible exit doesn't matter if there aren't alternative services. Interoperability is pointless if other applications don't offer something your app doesn't. Marketing to nostr users doesn't matter if you don't augment their agency as nostr users.
If I had to choose a single NIP that represents the mindset behind this kind of app, it would be NIP 89 A.K.A. "Recommended Application Handlers", which states:
Nostr's discoverability and transparent event interaction is one of its most interesting/novel mechanics. This NIP provides a simple way for clients to discover applications that handle events of a specific kind to ensure smooth cross-client and cross-kind interactions.
These handlers are the glue that holds nostr apps together. A single event, signed by the developer of an application (or by the application's own account) tells anyone who wants to know 1. what event kinds the app supports, 2. how to link to the app (if it's a client), and (if the pubkey also publishes a kind 10002), 3. which relays the app prefers.
As a sidenote, NIP 89 is currently focused more on clients, leaving DVMs, relays, signers, etc somewhat out in the cold. Updating 89 to include tailored listings for each kind of supporting app would be a huge improvement to the protocol. This, plus a good front end for navigating these listings (sorry nostrapp.link, close but no cigar) would obviate the evil centralized websites that curate apps based on arbitrary criteria.
Examples of this kind of app obviously include many kind 1 clients, as well as clients that attempt to bring the benefits of the nostr protocol and network to new use cases - whether long form content, video, image posts, music, emojis, recipes, project management, or any other "content type".
To drill down into one example, let's think for a moment about forms. What's so great about a forms app that is built on nostr? Well,
- There is a spec for forms and responses, which means that...
- Multiple clients can implement the same data format, allowing for credible exit and user choice, even of...
- Other products not focused on forms, which can still view, respond to, or embed forms, and which can send their users via NIP 89 to a client that does...
- Cryptographically sign forms and responses, which means they are self-authenticating and can be sent to...
- Multiple relays, which reduces the amount of trust necessary to be confident results haven't been deliberately "lost".
Show me a forms product that does all of those things, and isn't built on nostr. You can't, because it doesn't exist. Meanwhile, there are plenty of image hosts with APIs, streaming services, and bitcoin wallets which have basically the same levels of censorship resistance, interoperability, and network effect as if they weren't built on nostr.
It supports nostr
Notice I haven't said anything about whether relays, signers, blossom servers, software libraries, DVMs, and the accumulated addenda of the nostr ecosystem are nostr apps. Well, they are (usually).
This is the category of nostr app that gets none of the credit for doing all of the work. There's no question that they qualify as beautiful nostrcorns, because their value propositions are entirely meaningless outside of the context of nostr. Who needs a signer if you don't have a cryptographic identity you need to protect? DVMs are literally impossible to use without relays. How are you going to find the blossom server that will serve a given hash if you don't know which servers the publishing user has selected to store their content?
In addition to being entirely contextualized by nostr architecture, this type of nostr app is valuable because it does things "the nostr way". By that I mean that they don't simply try to replicate existing internet functionality into a nostr context; instead, they create entirely new ways of putting the basic building blocks of the internet back together.
A great example of this is how Nostr Connect, Nostr Wallet Connect, and DVMs all use relays as brokers, which allows service providers to avoid having to accept incoming network connections. This opens up really interesting possibilities all on its own.
So while I might hesitate to call many of these things "apps", they are certainly "nostr".
Appendix: it smells like a NINO
So, let's say you've created an app, but when you show it to people they politely smile, nod, and call it a NINO (Nostr In Name Only). What's a hacker to do? Well, here's your handy-dandy guide on how to wash that NINO stench off and Become a Nostr.
You app might be a NINO if:
- There's no NIP for your data format (or you're abusing NIP 78, 32, etc by inventing a sub-protocol inside an existing event kind)
- There's a NIP, but no one knows about it because it's in a text file on your hard drive (or buried in your project's repository)
- Your NIP imposes an incompatible/centralized/legacy web paradigm onto nostr
- Your NIP relies on trusted third (or first) parties
- There's only one implementation of your NIP (yours)
- Your core value proposition doesn't depend on relays, events, or nostr identities
- One or more relay urls are hard-coded into the source code
- Your app depends on a specific relay implementation to work (ahem, relay29)
- You don't validate event signatures
- You don't publish events to relays you don't control
- You don't read events from relays you don't control
- You use legacy web services to solve problems, rather than nostr-native solutions
- You use nostr-native solutions, but you've hardcoded their pubkeys or URLs into your app
- You don't use NIP 89 to discover clients and services
- You haven't published a NIP 89 listing for your app
- You don't leverage your users' web of trust for filtering out spam
- You don't respect your users' mute lists
- You try to "own" your users' data
Now let me just re-iterate - it's ok to be a NINO. We need NINOs, because nostr can't (and shouldn't) tackle every problem. You just need to decide whether your app, as a NINO, is actually contributing to the nostr ecosystem, or whether you're just using buzzwords to whitewash a legacy web software product.
If you're in the former camp, great! If you're in the latter, what are you waiting for? Only you can fix your NINO problem. And there are lots of ways to do this, depending on your own unique situation:
- Drop nostr support if it's not doing anyone any good. If you want to build a normal company and make some money, that's perfectly fine.
- Build out your nostr integration - start taking advantage of webs of trust, self-authenticating data, event handlers, etc.
- Work around the problem. Think you need a special relay feature for your app to work? Guess again. Consider encryption, AUTH, DVMs, or better data formats.
- Think your idea is a good one? Talk to other devs or open a PR to the nips repo. No one can adopt your NIP if they don't know about it.
- Keep going. It can sometimes be hard to distinguish a research project from a NINO. New ideas have to be built out before they can be fully appreciated.
- Listen to advice. Nostr developers are friendly and happy to help. If you're not sure why you're getting traction, ask!
I sincerely hope this article is useful for all of you out there in NINO land. Maybe this made you feel better about not passing the totally optional nostr app purity test. Or maybe it gave you some actionable next steps towards making a great NINON (Nostr In Not Only Name) app. In either case, GM and PV.
-
 @ da0b9bc3:4e30a4a9
2025-03-24 08:13:00
@ da0b9bc3:4e30a4a9
2025-03-24 08:13:00Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/923278
-
 @ 9e69e420:d12360c2
2025-01-30 12:23:04
@ 9e69e420:d12360c2
2025-01-30 12:23:04Tech stocks have taken a hit globally after China's DeepSeek launched a competitive AI chatbot at a much lower cost than US counterparts. This has stirred market fears of a $1.2 trillion loss across tech companies when trading opens in New York.
DeepSeek’s chatbot quickly topped download charts and surprised experts with its capabilities, developed for only $5.6 million.
The Nasdaq dropped over 3% in premarket trading, with major firms like Nvidia falling more than 10%. SoftBank also saw losses shortly after investing in a significant US AI venture.
Venture capitalist Marc Andreessen called it “AI’s Sputnik moment,” highlighting its potential impact on the industry.
![] (https://www.telegraph.co.uk/content/dam/business/2025/01/27/TELEMMGLPICT000409807198_17379939060750_trans_NvBQzQNjv4BqgsaO8O78rhmZrDxTlQBjdGLvJF5WfpqnBZShRL_tOZw.jpeg)
-
 @ 0fa80bd3:ea7325de
2025-01-30 04:28:30
@ 0fa80bd3:ea7325de
2025-01-30 04:28:30"Degeneration" or "Вырождение" ![[photo_2025-01-29 23.23.15.jpeg]]
A once-functional object, now eroded by time and human intervention, stripped of its original purpose. Layers of presence accumulate—marks, alterations, traces of intent—until the very essence is obscured. Restoration is paradoxical: to reclaim, one must erase. Yet erasure is an impossibility, for to remove these imprints is to deny the existence of those who shaped them.
The work stands as a meditation on entropy, memory, and the irreversible dialogue between creation and decay.
-
 @ 0fa80bd3:ea7325de
2025-01-29 15:43:42
@ 0fa80bd3:ea7325de
2025-01-29 15:43:42Lyn Alden - биткойн евангелист или евангелистка, я пока не понял
npub1a2cww4kn9wqte4ry70vyfwqyqvpswksna27rtxd8vty6c74era8sdcw83aThomas Pacchia - PubKey owner - X - @tpacchia
npub1xy6exlg37pw84cpyj05c2pdgv86hr25cxn0g7aa8g8a6v97mhduqeuhgplcalvadev - Shopstr
npub16dhgpql60vmd4mnydjut87vla23a38j689jssaqlqqlzrtqtd0kqex0nkqCalle - Cashu founder
npub12rv5lskctqxxs2c8rf2zlzc7xx3qpvzs3w4etgemauy9thegr43sf485vgДжек Дорси
npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m21 ideas
npub1lm3f47nzyf0rjp6fsl4qlnkmzed4uj4h2gnf2vhe3l3mrj85vqks6z3c7lМного адресов. Хз кто надо сортировать
https://github.com/aitechguy/nostr-address-bookФиатДжеф - создатель Ностр - https://github.com/fiatjaf
npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6EVAN KALOUDIS Zues wallet
npub19kv88vjm7tw6v9qksn2y6h4hdt6e79nh3zjcud36k9n3lmlwsleqwte2qdПрограммер Коди https://github.com/CodyTseng/nostr-relay
npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wlAnna Chekhovich - Managing Bitcoin at The Anti-Corruption Foundation https://x.com/AnyaChekhovich
npub1y2st7rp54277hyd2usw6shy3kxprnmpvhkezmldp7vhl7hp920aq9cfyr7 -
 @ fbf0e434:e1be6a39
2025-03-24 07:37:41
@ fbf0e434:e1be6a39
2025-03-24 07:37:41黑客即命运:四个支点推动未来的杠杆
在《Why Software is Eating the World》中,Marc Andreessen 指出,软件的扩张不仅是一场技术革命,更是一场社会变革。我们深以为然。但 DoraHacks 相信真正改变世界的不只是软件,而是一群愿意动手解决问题的黑客(Hackers)。
DoraHacks 正在构建 Hacker Movement —— 一个以自由、开源、技术为武器的全球创新网络。我们认为这个运动的终点不是某种“Web3.0”神话,也不是一个新冷战时代的技术出口,而是一场社会的重构,是对“什么值得被构建”这一问题的深度回应。
在这个过程中,Dora Ventures 是辅助 DoraHacks 协调与捕获价值的资本引擎。Dora Ventures 当前的工作将围绕以下四个方面展开:
一、FDA 自由社会 (BioHack)
黑客社会的健康自由宣言:解锁生命技术的市场机制
回顾历史,每一次真正的技术突破,都伴随着对既有范式的挑战。今天,医疗健康领域依然是人类最受制于官僚主义的地方 —— 一个新药从实验室走向病人,往往需要十年时间和几十亿美元的投入,绝大多数创新止步于此。
FDA Free Society,并不是呼吁无政府主义,而是呼吁一种更具活力、更以患者为中心的健康和生物科技创新体系。
我们看到的问题:
- FDA的审批周期与风险厌恶机制正在扼杀潜在的突破性治疗;
- 大药企的市场垄断让药品定价脱离现实,限制竞争;
- 病人的“尝试权”(Right to Try)在监管框架下被边缘化;
- 小型生物科技初创公司面对高昂试验成本几乎没有生存空间。
我们相信的解决方向:
- 市场驱动的健康创新机制:把研发、试验和使用的决策权更多交还给患者、医生和创业者;
- 让创新回归第一性原理:不是“通过审批”,而是“是否有效”;
- 为 Right to Try 正名:真正的风险不是尝试未经审批的疗法,而是死于等待;
- 打造有竞争力的生物初创生态:帮助小团队也有机会改变世界,而不只是为大药厂打工。
- 软件和人工智能驱动的生物科技:生物科技和软件的结合驱动全新的生物科技产品。
我们相信,药物研发的未来,不属于某个监管机构,也不属于市值5000亿的大公司,而属于一群不愿等待的创新者。
FDA Free Society 是对“技术进步必须服从监管”的有力反击,是对“创新必须通过审批”的结构性质疑。我们押注这个方向,是因为它比“创新”更稀缺——它关乎人类对生存权的重新主张。
二、开源量子计算基础设施(Open Source Quantum)
量子软件的开源狂潮,是今天的以太坊2015年
Arthur C. Clarke 曾说:“任何足够先进的技术,看起来都像是魔法。” 量子计算就是这样一种技术。但问题在于,魔法要成为工具,必须走向可编程、可复现、可协作 —— 换句话说,它需要“开源”。
Dora Ventures 对量子计算的投资逻辑很清晰:量子计算正走向它的“智能合约时刻”。硬件进入工程优化周期,软件和工具层尚属一片荒芜,但这正是黑客的黄金年代。
我们关注的几个关键趋势:
- 开源量子编译器与转译器:打通经典与量子系统的语言障碍;
- 量子密码学:利用量子力学的原理构建全新的加密系统;
- 量子软件应用:我们相信量子计算软件和应用可以在人工智能、生物科技、区块链等技术的进步中发挥巨大的价值,直接或间接影响金融、物流、制药、国防、太空探索等重要领域。
我们不仅是观察者,更是建设者。通过举办黑客松、资助和投资量子开源软件项目、开展量子密码学的研究和生态发展,我们参与这个时代最具颠覆性的计算平台的构建。
三、消费级加密应用(Consumer Crypto)
胖应用的春天已至:Crypto 将赢得最后10亿用户
如果你理解历史,你会明白今天的 Crypto 不是互联网的“平行世界”,而是互联网故事的下一个篇章。
1990年代,HTTP 和 TCP/IP 改变了信息分发; 2000年代,Web 应用改变了商业与社交; 2010年代,移动端应用重塑了人类行为; 2020年代,是 Crypto 应用真正走向大众的十年。
基础设施已充分,胖应用正在破壳而出。
Dora Ventures 最核心的判断是:谁能抓住第一个亿级用户的Crypto应用场景,谁将书写Web3时代的Paypal和微信故事。
- 稳定币合规化将使 USDC 成为数字美元;
- 去中心化社交和加密支付的全球化催生比特币和 Web3 支付的“ VISA 网络”;
- 大应用链基建将通过 Move 语言和极简化工具降低用户门槛;
- 链上原生经济系统将实现创作者直接变现、社区协作分润。
想象这个场景: 一个住在纽约的人通过链上音乐会平台(KYD Labs)使用快速Move区块链网络(Aptos)的 Circle USDC 购买今晚的演唱会门票,一个阿根廷的居民每天去咖啡馆用闪电网络上的比特币“聪”购买拿铁,在去中心化社交媒体(Yakihonne)与朋友分账单,这些都会在今年真实发生。我们不只是投资协议,而是投资体验新范式的创造者。
四、全自动化组织(Agentic Organizations)
组织将成为智能体,DAO将成为大型语言模型的组织形态
2022年,Sam Altman 重构了“工具”的定义;2025年,我们将重构“组织”的定义。
我们认为,未来组织不是由人构成的矩阵结构,而是由Agent协作而成的智能系统。
Agent 是新的工作单元,它不眠不休、持续学习、自动调度。它不是增强人类的工具,而是自动化组织的大脑。
一些例子:
- DAO Agent 系统将自动执行治理流程,并保护参与者隐私;
- Smart Widget 框架让开发者用三行代码部署社交、支付、交易型 Agent ;
- 隐私协议和隐私应用在自动化组织中成为主流;
- 黑客松涌现出大量加密 Agent。
AI + 区块链不是 Buzzword ,而是组织智能化的起点。
过去我们说“公司是信息处理的机器”,未来我们会说“ DAO 是 Agent 运行的网络”。我们正在进入一个无需CEO的公司、无需审批的流程、无需办公室的全自动化组织时代。
尾声:我们下注在拥有“BUIDL自由”的人类
这四个方向——FDA Free Society、Open Source Quantum、Consumer Crypto、Agentic Organizations,不是我们幻想的未来,而是已经开始发生的未来。
Dora Ventures不是下注在技术上,而是下注在一群不服从的Builder身上。他们愿意解决真正的问题,质疑现有体制,构建新的秩序。他们相信世界可以不同,并愿意动手去实现它。
黑客运动正在吞噬世界,在人工智能的时代,人类必将成为 Hacker ,用代码,用治理,用想象力,创造一个值得居住的世界。
-
 @ a012dc82:6458a70d
2025-03-24 06:54:13
@ a012dc82:6458a70d
2025-03-24 06:54:13Bitcoin, the original cryptocurrency, has once again captured headlines and investor interest by reaching a new record high, surpassing its previous peak from November 2021. This remarkable resurgence underscores the volatile yet unstoppable journey of Bitcoin, reflecting broader trends in the cryptocurrency market and global finance. Beyond its financial implications, this surge represents a significant cultural and technological milestone, highlighting the increasing integration of digital currencies into mainstream financial systems and the growing public interest in decentralized finance solutions. This article delves into the factors behind Bitcoin's latest surge, its implications, and what the future may hold for this digital asset, considering the complex interplay between market dynamics, technological advancements, and regulatory landscapes.
Table of Contents
-
The New Peak: Bitcoin's Latest Achievement
-
Understanding Bitcoin's Appeal
-
Catalysts for the Recent Surge
-
Institutional Acceptance and ETFs
-
Economic Environment
-
-
Is the Surge Sustainable?
-
Regulatory Landscape and Future Prospects
- Conclusion
- FAQs
The New Peak: Bitcoin's Latest Achievement
After more than two years, Bitcoin has shattered its previous record, climbing to just under $69,000 before stabilizing around $64,000. This surge has propelled Bitcoin's market valuation to approximately $1.3 trillion, representing a significant portion of the total $2.6 trillion cryptocurrency market. This achievement is not just a milestone for Bitcoin but also a testament to the growing acceptance and maturation of cryptocurrencies as a whole. The new peak is a reflection of the enduring faith of long-term investors and the influx of new participants drawn by Bitcoin's proven resilience and potential for substantial returns. This landmark event is not merely about surpassing a numerical threshold but symbolizes the culmination of years of development, debate, and adoption that have expanded the boundaries of what is possible in the realm of digital finance. It prompts a reevaluation of Bitcoin's role not only as a speculative asset but as a foundational component of a new, evolving digital economy.
Understanding Bitcoin's Appeal
Bitcoin's inception in 2008 by the enigmatic Satoshi Nakamoto introduced a revolutionary concept: a digital currency enabling direct transactions without the need for traditional financial institutions. The core innovation of Bitcoin, the blockchain, solved the "double spend" problem inherent to digital currencies, ensuring secure, transparent, and decentralized transactions. This anti-authoritarian stance, combined with the promise of lower transaction fees and resistance to inflation, has fueled Bitcoin's popularity. The appeal of Bitcoin extends beyond its technological underpinnings to embody a broader desire for financial autonomy and privacy. It challenges conventional banking systems and offers an alternative for individuals disillusioned with traditional financial institutions. Bitcoin's decentralized nature appeals to those seeking freedom from governmental oversight and inflationary policies, positioning it as a symbol of financial empowerment and self-sovereignty. As Bitcoin continues to evolve, its appeal broadens, attracting a diverse group of users from libertarians to tech enthusiasts, and from small investors to large institutional players.
Catalysts for the Recent Surge
Several factors have contributed to Bitcoin's recent price explosion:
Institutional Acceptance and ETFs
The approval of Bitcoin exchange-traded funds (ETFs) by the US financial regulator marked a significant step towards institutional acceptance. These ETFs allow investors to gain exposure to Bitcoin without directly purchasing the digital asset, reducing barriers to entry and signaling a new level of market maturity. This development is a clear indication of the growing recognition of Bitcoin's value proposition by mainstream financial entities. It reflects a broader shift in perception among institutional investors, who are increasingly viewing Bitcoin and other cryptocurrencies not just as speculative investments but as legitimate components of diversified portfolios. The introduction of ETFs has facilitated this transition by providing a familiar and regulated framework for investing in Bitcoin, thereby attracting a new wave of institutional capital into the cryptocurrency market.
Economic Environment
The low-interest-rate environment since the 2008 financial crisis has driven investors towards riskier assets, including cryptocurrencies, in search of higher returns. Additionally, Bitcoin is increasingly viewed as an "inflation hedge," similar to gold, appealing to those wary of central bank policies and currency devaluation. The economic landscape has been further complicated by the global pandemic, geopolitical tensions, and supply chain disruptions, leading to increased market volatility and a renewed focus on alternative assets like Bitcoin. As traditional financial systems show signs of strain and governments continue to engage in unprecedented levels of monetary expansion, Bitcoin's fixed supply and decentralized nature offer a compelling alternative for those looking to preserve value and hedge against inflationary pressures.
Is the Surge Sustainable?
While the excitement around Bitcoin's new record is palpable, questions remain about the sustainability of this surge. Historical patterns suggest that parabolic increases in Bitcoin's price are often followed by corrections. Factors such as profit-taking by early investors and the eventual saturation of new buyers could lead to a price consolidation. However, the upcoming "halving" event, which reduces the Bitcoin reward for mining, could counterbalance these pressures by reducing the new supply of Bitcoin and potentially driving up its price. The sustainability of Bitcoin's price surge also hinges on broader market dynamics, including technological advancements, regulatory developments, and shifts in investor sentiment. As Bitcoin becomes more integrated into the global financial system, its price movements are increasingly influenced by a complex interplay of factors, making its future trajectory difficult to predict. Nonetheless, the underlying principles of scarcity, security, and decentralization that underpin Bitcoin provide a strong foundation for its long-term value proposition.
Regulatory Landscape and Future Prospects
The regulatory environment continues to evolve, with increased scrutiny in the UK, EU, and US. While tighter regulations may introduce more stability to the market, they could also restrict some of the freedoms that make cryptocurrencies attractive. Nevertheless, the recent approval of Bitcoin ETFs in the US has been a positive development, potentially paving the way for more regulated crypto assets and attracting a broader base of investors. The future of Bitcoin and the broader cryptocurrency market will be significantly shaped by regulatory decisions, technological innovations, and shifts in global economic conditions. As regulators around the world grapple with the challenges and opportunities presented by cryptocurrencies, the outcome of these deliberations will have far-reaching implications for the adoption, utility, and value of Bitcoin. Despite the uncertainties, the ongoing developments in the regulatory landscape signify a growing recognition of the importance of cryptocurrencies and the need for a balanced approach that ensures security, transparency, and innovation.
Conclusion
Bitcoin's latest record high is more than just a numerical milestone; it represents the ongoing evolution and resilience of the cryptocurrency market. While challenges remain, including regulatory hurdles and market volatility, Bitcoin's journey continues to captivate investors, technologists, and financial analysts alike. As the world becomes increasingly digital, the role of cryptocurrencies like Bitcoin in the global financial ecosystem is likely to grow, making its journey an unstoppable force in the changing landscape of money and investment. The path ahead for Bitcoin is fraught with challenges and opportunities, but its recent achievements underscore its potential to redefine the boundaries of finance, technology, and societal norms. As we look to the future, Bitcoin's journey remains a compelling narrative of innovation, speculation, and the relentless pursuit of a decentralized and empowered financial future.
FAQs
What caused Bitcoin to reach a new record high? Bitcoin's recent surge to a new record high was influenced by several factors, including institutional acceptance, the approval of Bitcoin ETFs, the economic environment fostering a search for inflation hedges, and technological advancements in the cryptocurrency space.
What is a Bitcoin ETF, and why is it important? A Bitcoin ETF (Exchange-Traded Fund) allows investors to gain exposure to Bitcoin's price without owning the actual cryptocurrency. This is important because it provides a regulated and accessible way for institutional and retail investors to invest in Bitcoin, potentially increasing its adoption and market stability.
Can Bitcoin's price surge be sustained? While Bitcoin's price has historically been volatile, factors such as its upcoming halving event, institutional investment, and its role as a perceived inflation hedge may support its value. However, market corrections are common following significant surges, and investor caution is advised.
How do regulatory changes affect Bitcoin's price? Regulatory changes can have significant impacts on Bitcoin's price. Positive regulatory developments, such as the approval of Bitcoin ETFs, can boost investor confidence, while stricter regulations may limit trading or use, potentially affecting the price negatively.
What is the "halving" event, and why is it significant? The "halving" is an event that occurs approximately every four years, where the reward for mining new Bitcoin blocks is halved, effectively reducing the rate at which new Bitcoins are created. This event can lead to increased prices due to reduced supply and increased scarcity.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co/
Youtube: @thebitcoinlibertarian
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
Get Orange Pill App And Connect With Bitcoiners In Your Area. Stack Friends Who Stack Sats link: https://signup.theorangepillapp.com/opa/croxroad
Buy Bitcoin Books At Konsensus Network Store. 10% Discount With Code “21croxroad” link: https://bitcoinbook.shop?ref=21croxroad
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 0fa80bd3:ea7325de
2025-01-29 14:44:48
@ 0fa80bd3:ea7325de
2025-01-29 14:44:48![[yedinaya-rossiya-bear.png]]
1️⃣ Be where the bear roams. Stay in its territory, where it hunts for food. No point setting a trap in your backyard if the bear’s chilling in the forest.
2️⃣ Set a well-hidden trap. Bury it, disguise it, and place the bait right in the center. Bears are omnivores—just like secret police KGB agents. And what’s the tastiest bait for them? Money.
3️⃣ Wait for the bear to take the bait. When it reaches in, the trap will snap shut around its paw. It’ll be alive, but stuck. No escape.
Now, what you do with a trapped bear is another question... 😏
-
 @ 0fa80bd3:ea7325de
2025-01-29 05:55:02
@ 0fa80bd3:ea7325de
2025-01-29 05:55:02The land that belongs to the indigenous peoples of Russia has been seized by a gang of killers who have unleashed a war of extermination. They wipe out anyone who refuses to conform to their rules. Those who disagree and stay behind are tortured and killed in prisons and labor camps. Those who flee lose their homeland, dissolve into foreign cultures, and fade away. And those who stand up to protect their people are attacked by the misled and deceived. The deceived die for the unchecked greed of a single dictator—thousands from both sides, people who just wanted to live, raise their kids, and build a future.
Now, they are forced to make an impossible choice: abandon their homeland or die. Some perish on the battlefield, others lose themselves in exile, stripped of their identity, scattered in a world that isn’t theirs.
There’s been endless debate about how to fix this, how to clear the field of the weeds that choke out every new sprout, every attempt at change. But the real problem? We can’t play by their rules. We can’t speak their language or use their weapons. We stand for humanity, and no matter how righteous our cause, we will not multiply suffering. Victory doesn’t come from matching the enemy—it comes from staying ahead, from using tools they haven’t mastered yet. That’s how wars are won.
Our only resource is the will of the people to rewrite the order of things. Historian Timothy Snyder once said that a nation cannot exist without a city. A city is where the most active part of a nation thrives. But the cities are occupied. The streets are watched. Gatherings are impossible. They control the money. They control the mail. They control the media. And any dissent is crushed before it can take root.
So I started asking myself: How do we stop this fragmentation? How do we create a space where people can rebuild their connections when they’re ready? How do we build a self-sustaining network, where everyone contributes and benefits proportionally, while keeping their freedom to leave intact? And more importantly—how do we make it spread, even in occupied territory?
In 2009, something historic happened: the internet got its own money. Thanks to Satoshi Nakamoto, the world took a massive leap forward. Bitcoin and decentralized ledgers shattered the idea that money must be controlled by the state. Now, to move or store value, all you need is an address and a key. A tiny string of text, easy to carry, impossible to seize.
That was the year money broke free. The state lost its grip. Its biggest weapon—physical currency—became irrelevant. Money became purely digital.
The internet was already a sanctuary for information, a place where people could connect and organize. But with Bitcoin, it evolved. Now, value itself could flow freely, beyond the reach of authorities.
Think about it: when seedlings are grown in controlled environments before being planted outside, they get stronger, survive longer, and bear fruit faster. That’s how we handle crops in harsh climates—nurture them until they’re ready for the wild.
Now, picture the internet as that controlled environment for ideas. Bitcoin? It’s the fertile soil that lets them grow. A testing ground for new models of interaction, where concepts can take root before they move into the real world. If nation-states are a battlefield, locked in a brutal war for territory, the internet is boundless. It can absorb any number of ideas, any number of people, and it doesn’t run out of space.
But for this ecosystem to thrive, people need safe ways to communicate, to share ideas, to build something real—without surveillance, without censorship, without the constant fear of being erased.
This is where Nostr comes in.
Nostr—"Notes and Other Stuff Transmitted by Relays"—is more than just a messaging protocol. It’s a new kind of city. One that no dictator can seize, no corporation can own, no government can shut down.
It’s built on decentralization, encryption, and individual control. Messages don’t pass through central servers—they are relayed through independent nodes, and users choose which ones to trust. There’s no master switch to shut it all down. Every person owns their identity, their data, their connections. And no one—no state, no tech giant, no algorithm—can silence them.
In a world where cities fall and governments fail, Nostr is a city that cannot be occupied. A place for ideas, for networks, for freedom. A city that grows stronger the more people build within it.
-
 @ 9e69e420:d12360c2
2025-01-26 15:26:44
@ 9e69e420:d12360c2
2025-01-26 15:26:44Secretary of State Marco Rubio issued new guidance halting spending on most foreign aid grants for 90 days, including military assistance to Ukraine. This immediate order shocked State Department officials and mandates “stop-work orders” on nearly all existing foreign assistance awards.
While it allows exceptions for military financing to Egypt and Israel, as well as emergency food assistance, it restricts aid to key allies like Ukraine, Jordan, and Taiwan. The guidance raises potential liability risks for the government due to unfulfilled contracts.
A report will be prepared within 85 days to recommend which programs to continue or discontinue.
-
 @ 9e69e420:d12360c2
2025-01-26 01:31:31
@ 9e69e420:d12360c2
2025-01-26 01:31:31Chef's notes
arbitray
- test
- of
- chefs notes
hedding 2
Details
- ⏲️ Prep time: 20
- 🍳 Cook time: 1 hour
- 🍽️ Servings: 5
Ingredients
- Test ingredient
- 2nd test ingredient
Directions
- Bake
- Cool
-
 @ 9e69e420:d12360c2
2025-01-25 22:16:54
@ 9e69e420:d12360c2
2025-01-25 22:16:54President Trump plans to withdraw 20,000 U.S. troops from Europe and expects European allies to contribute financially to the remaining military presence. Reported by ANSA, Trump aims to deliver this message to European leaders since taking office. A European diplomat noted, “the costs cannot be borne solely by American taxpayers.”
The Pentagon hasn't commented yet. Trump has previously sought lower troop levels in Europe and had ordered cuts during his first term. The U.S. currently maintains around 65,000 troops in Europe, with total forces reaching 100,000 since the Ukraine invasion. Trump's new approach may shift military focus to the Pacific amid growing concerns about China.
-
 @ 6be5cc06:5259daf0
2025-01-21 23:17:29
@ 6be5cc06:5259daf0
2025-01-21 23:17:29A seguir, veja como instalar e configurar o Privoxy no Pop!_OS.
1. Instalar o Tor e o Privoxy
Abra o terminal e execute:
bash sudo apt update sudo apt install tor privoxyExplicação:
- Tor: Roteia o tráfego pela rede Tor.
- Privoxy: Proxy avançado que intermedia a conexão entre aplicativos e o Tor.
2. Configurar o Privoxy
Abra o arquivo de configuração do Privoxy:
bash sudo nano /etc/privoxy/configNavegue até a última linha (atalho:
Ctrl+/depoisCtrl+Vpara navegar diretamente até a última linha) e insira:bash forward-socks5 / 127.0.0.1:9050 .Isso faz com que o Privoxy envie todo o tráfego para o Tor através da porta 9050.
Salve (
CTRL+OeEnter) e feche (CTRL+X) o arquivo.
3. Iniciar o Tor e o Privoxy
Agora, inicie e habilite os serviços:
bash sudo systemctl start tor sudo systemctl start privoxy sudo systemctl enable tor sudo systemctl enable privoxyExplicação:
- start: Inicia os serviços.
- enable: Faz com que iniciem automaticamente ao ligar o PC.
4. Configurar o Navegador Firefox
Para usar a rede Tor com o Firefox:
- Abra o Firefox.
- Acesse Configurações → Configurar conexão.
- Selecione Configuração manual de proxy.
- Configure assim:
- Proxy HTTP:
127.0.0.1 - Porta:
8118(porta padrão do Privoxy) - Domínio SOCKS (v5):
127.0.0.1 - Porta:
9050
- Proxy HTTP:
- Marque a opção "Usar este proxy também em HTTPS".
- Clique em OK.
5. Verificar a Conexão com o Tor
Abra o navegador e acesse:
text https://check.torproject.org/Se aparecer a mensagem "Congratulations. This browser is configured to use Tor.", a configuração está correta.
Dicas Extras
- Privoxy pode ser ajustado para bloquear anúncios e rastreadores.
- Outros aplicativos também podem ser configurados para usar o Privoxy.
-
 @ 502ab02a:a2860397
2025-03-24 04:13:11
@ 502ab02a:a2860397
2025-03-24 04:13:11วันนี้จะมาเล่าเรื่องการทลายและจับกุมเครือข่ายน้ำมันมะกอกปลอม เบื้องหลังการต่อสู้ในโลกของอุตสาหกรรมอาหาร กันครับ
ด้วยความที่ว่าน้ำมันมะกอก Extra Virgin ถูกยกย่องให้เป็นหนึ่งในน้ำมันที่มีคุณภาพสูงและเป็นสัญลักษณ์ของความมีสุขภาพที่ดีทั่วโลก แถมด้วยรสชาติที่ซับซ้อน กลิ่นหอมเฉพาะตัว มาพร้อมคุณค่าทางโภชนาการที่หลากหลาย ไม่ต้องสงสัยเลยว่าทำไมคนทั้งโลกจึงยินดีจ่ายในราคาที่ค่อนข้างสูง
แล้วไอ้ด้วยความต้องการในสินค้าที่มีมูลค่าสูงนี่ละครับ กลายเป็นช่องทางให้กับกลุ่มอาชญากรรมที่มุ่งหวังหากำไรจากการหลอกลวงผู้บริโภค ด้วยการผลิตน้ำมันมะกอกปลอมที่ผ่านการเจือจางหรือดัดแปลงให้ดูเหมือนของแท้ ในเครือข่ายนี้มีการใช้งานเทคนิคและสารเติมแต่งเพื่อเลียนแบบคุณสมบัติของน้ำมันมะกอกแท้ เช่น การปรับเปลี่ยนกลิ่น รสชาติ และคุณสมบัติการแข็งตัวเมื่อแช่เย็น ซึ่งเคยเป็นวิธีตรวจสอบที่ง่ายต่อการแยกแยะของผลิตภัณฑ์แท้ แต่ด้วยเทคนิคใหม่ ๆ ที่ถูกพัฒนาขึ้น ผู้ปลอมแปลงสามารถทำให้ผลิตภัณฑ์ปลอมเหล่านี้ผ่านการตรวจสอบเบื้องต้นได้อย่างไร้ร่องรอย
ข้อมูลจากหลายรายงานของหน่วยงานกำกับดูแลอาหารในยุโรปและสหรัฐอเมริกาเผยว่าขบวนการปลอมแปลงน้ำมันมะกอกเกิดขึ้นในหลายประเทศในแถบเมดิเตอร์เรเนียน โดยเฉพาะในอิตาลี ซึ่งเป็นศูนย์กลางของการผลิตน้ำมันมะกอก
กลุ่มอาชญากรรมในภูมิภาคเหล่านี้ได้นำเอาวิธีการผลิตที่ผิดกฎหมายและการใช้สารเติมแต่งราคาถูกมาเจือจางกับน้ำมันมะกอกแท้ ทำให้ผู้บริโภคไม่สามารถตรวจสอบคุณภาพของผลิตภัณฑ์ได้ด้วยการทดสอบง่าย ๆ เช่น การแช่ตู้เย็นเพื่อตรวจดูการแข็งตัวได้อีกต่อไป (งว่อออ มีอัพเดท patch)
หน่วยงานตำรวจและหน่วยงานกำกับดูแลในอิตาลีร่วมกับหน่วยงานระดับนานาชาติ เช่น EFSA (European Food Safety Authority) และ FDA (Food and Drug Administration) ของสหรัฐอเมริกา ได้ร่วมมือกันเปิดเผยและจับกุมเครือข่ายน้ำมันมะกอกปลอมที่มีความซับซ้อนและขนาดใหญ่ หนึ่งในการจับกุมครั้งใหญ่เกิดขึ้นในปี 2017 เมื่อเจ้าหน้าที่ตำรวจอิตาลีร่วมกับหน่วยงานสอบสวนระดับนานาชาติได้ดำเนินการบุกค้นโรงงานผลิตลับในพื้นที่ชนบทของอิตาลี ที่มีหลักฐานชัดเจนว่ามีการผลิตน้ำมันมะกอกปลอมในปริมาณมหาศาล
เจ้าหน้าที่ได้ค้นพบโกดังที่ถูกซ่อนอยู่ในเขตอุตสาหกรรมที่มีการจัดเก็บถังน้ำมันจำนวนมาก ซึ่งบรรจุผลิตภัณฑ์ที่ถูกเจือจางด้วยน้ำมันพืชราคาถูก เช่น น้ำมันถั่วเหลือง น้ำมันปาล์ม และน้ำมันคาโนลา รวมถึงการเติมสารเคมีที่ช่วยปรับปรุงลักษณะทางกายภาพ เช่น ขี้ผึ้งพืช (Candelilla Wax หรือ Carnauba Wax) เพื่อให้ผลิตภัณฑ์มีคุณสมบัติการแข็งตัวเมื่อนำไปแช่เย็น เหล่านี้เป็นเทคนิคที่ผู้ปลอมแปลงพัฒนาขึ้นเพื่อเลี่ยงการตรวจสอบด้วยวิธีดั้งเดิมที่เคยใช้แยกแยะน้ำมันมะกอกแท้กับปลอมได้
การจับกุมในครั้งนั้นเป็นการร่วมมือระหว่างเจ้าหน้าที่ตำรวจอิตาลีและหน่วยงานสอบสวนของสหภาพยุโรป ที่ได้ใช้เทคโนโลยีการตรวจสอบขั้นสูงและการวิเคราะห์ทางเคมีในห้องปฏิบัติการ เพื่อพิสูจน์ว่าผลิตภัณฑ์ที่ถูกบรรจุในขวดพร้อมฉลากที่หลอกลวงนั้นไม่ได้มีคุณภาพตามมาตรฐานของน้ำมันมะกอก Extra Virgin ขึ้นจริง เจ้าหน้าที่ได้จับกุมผู้ต้องหาและยึดทรัพย์สินในมูลค่าหลายร้อยล้านยูโร จากนั้นคดีนี้ได้ถูกนำเข้าสู่กระบวนการไต่สวนในศาลอิตาลี ซึ่งมีการลงโทษผู้เกี่ยวข้องด้วยโทษจำคุกหลายปีและการปรับเงินจำนวนมหาศาล
ในกระบวนการไต่สวน เจ้าหน้าที่ได้เปิดเผยว่าขบวนการนี้ไม่ได้ดำเนินการโดยบุคคลเพียงไม่กี่คนเท่านั้น แต่เป็นเครือข่ายขนาดใหญ่ที่มีการเชื่อมโยงกับกลุ่มมาเฟียอย่าง Cosa Nostra และ ’Ndrangheta ซึ่งเป็นกลุ่มอาชญากรรมที่มีอิทธิพลทั้งในประเทศและต่างประเทศ กลุ่มเหล่านี้มีบทบาทในการควบคุมการผลิต การจัดจำหน่าย และการขนส่งน้ำมันมะกอกปลอมผ่านเส้นทางลับที่ซับซ้อน ทั้งในรูปแบบของบริษัทหน้ากากและระบบการฟอกเงินที่มีความซับซ้อนสูง
ในปูมหลังของกลุ่มอาชญากรรมที่มีอิทธิพลในอิตาลี อย่างเช่น Cosa Nostra และ ’Ndrangheta เนี่ยครับ ถือเป็นประวัติศาสตร์ที่สลับซับซ้อนและเต็มไปด้วยความรุนแรง ความขัดแย้ง และกลยุทธ์ที่แยบยลในการดำเนินธุรกิจผิดกฎหมายที่กระจายไปทั่วโลก โดยเฉพาะการจับกุมครั้งใหญ่ในวงการปลอมแปลงน้ำมันมะกอกที่เรากำลังพูดถึง
Cosa Nostra หรือที่รู้จักกันในชื่อ “มาเฟียซิซิลี” หรือว่า The Sicilian Mafia ถือเป็นกลุ่มอาชญากรรมที่เก่าแก่ที่สุดและมีชื่อเสียงที่สุดในอิตาลี และมีอิทธิพลอย่างมากในโลกอาชญากรรมระหว่างประเทศ ประวัติของ Cosa Nostra เต็มไปด้วยความรุนแรงและการควบคุมธุรกิจผิดกฎหมายในหลายด้าน ไม่ว่าจะเป็นการค้ามนุษย์ การค้าผิดกฎหมาย และการติดสินบนเจ้าหน้าที่ของรัฐ สิ่งที่ทำให้ Cosa Nostra น่าสะพรึงกลัวคือวิธีการที่พวกเขาควบคุมแหล่งธุรกิจทั้งในอิตาลีและในต่างประเทศด้วยการใช้ความรุนแรงและการหลอกลวง
หนึ่งในคดีที่ทำให้ชื่อเสียงของ Cosa Nostra ติดตรึงในใจผู้คนทั่วโลกคือคดีฆาตกรรม Giovanni Falcone และ Paolo Borsellino ผู้พิพากษาที่ทำงานอย่างหนักเพื่อปราบปรามมาเฟียซิซิลีในช่วงปี 1990 โดยเฉพาะการต่อสู้กับ Cosa Nostra จนกระทั่งทั้งสองถูกลอบสังหารอย่างโหดเหี้ยมในเหตุการณ์ระเบิดที่เกิดขึ้นในปี 1992 การฆาตกรรมนี้ทำให้ผู้คนในอิตาลีและทั่วโลกตระหนักถึงพลังอำนาจและอิทธิพลของ Cosa Nostra ที่สามารถกระทำการรุนแรงได้แม้กระทั่งกับบุคคลในระดับสูง ขอเสริมให้ว่า Giovanni Falcone เป็นผู้พิพากษาและนักสืบที่มีบทบาทสำคัญในการทำลายเครือข่าย Cosa Nostra เขาเป็นผู้นำในการสร้างทีมสอบสวนที่เรียกว่า “Capaci Trial” และการวางแผนปฏิบัติการที่มุ่งหวังจะทำลายการกระทำผิดของมาเฟีย ซึ่งในที่สุดเขาก็เสียชีวิตจากการระเบิดรถยนต์ที่วางกับดักไว้โดยสมาชิก Cosa Nostra ในปี 1992 Paolo Borsellino ก็เป็นผู้พิพากษาที่ทำงานร่วมกับ Falcone ในการต่อสู้กับกลุ่มมาเฟีย Cosa Nostra และมีบทบาทสำคัญในการดำเนินการสอบสวนและพิจารณาคดีที่เกี่ยวข้องกับการกระทำผิดของมาเฟีย แต่เขาก็ถูกสังหารในเหตุการณ์ระเบิดรถยนต์อีกครั้งในปีเดียวกันกับการตายของ Falcone ซึ่งเกิดขึ้นไม่นานหลังจากที่ Falcone ถูกฆ่าตาย
ส่วน ’Ndrangheta ซึ่งมีต้นกำเนิดในแคว้นคาลาเบรีย (Calabria) ในอิตาลี ถือเป็นอีกหนึ่งกลุ่มที่มีอิทธิพลและความน่ากลัวไม่แพ้กัน แม้ว่าในช่วงแรก ’Ndrangheta จะไม่ได้มีชื่อเสียงโด่งดังเท่า Cosa Nostra แต่ในปัจจุบันกลุ่มนี้ถือว่าเป็นหนึ่งในเครือข่ายอาชญากรรมที่ใหญ่ที่สุดในโลก โดยเฉพาะในการควบคุมการค้ายาเสพติดระดับนานาชาติ และการกระทำผิดกฎหมายเกี่ยวกับการฟอกเงิน กลุ่มนี้ไม่ได้จำกัดการดำเนินงานแค่ในอิตาลี แต่ได้กระจายเครือข่ายไปทั่วโลก โดยเฉพาะใน ยุโรป และ อเมริกาเหนือ ซึ่งได้กลายเป็นพลังที่ยากจะหยุดยั้งได้
การทำธุรกิจของ ’Ndrangheta นั้นมีการใช้ความรุนแรงในการรักษาความมั่นคงและการแทรกซึมในระบบเศรษฐกิจ โดยเฉพาะในวงการการก่อสร้างและธุรกิจที่เกี่ยวข้องกับทรัพย์สิน พวกเขามีอิทธิพลอย่างมากในอุตสาหกรรมบางชนิด เช่น การค้ายาเสพติดที่มีมูลค่าสูง ซึ่งการควบคุมและการปราบปรามของพวกเขาทำให้เกิดความตื่นกลัวในทุกภาคส่วน
เคสดังๆ ที่ทำให้ ’Ndrangheta น่าสะพรึงกลัวคือการควบคุมการค้ายาเสพติดในตลาดยุโรป การที่พวกเขามีเครือข่ายกว้างขวางและการเชื่อมโยงกับกลุ่มอาชญากรระหว่างประเทศทำให้พวกเขามีอำนาจในการจัดการและกระจายยาเสพติดได้อย่างไม่มีที่สิ้นสุด อย่างในปี 2007 กลุ่ม ’Ndrangheta ถูกกล่าวหาว่ามีส่วนเกี่ยวข้องในการค้ายาเสพติดโคเคนมูลค่าหลายพันล้านดอลลาร์ โดยพวกเขาสามารถหลีกเลี่ยงการตรวจจับจากหน่วยงานตำรวจได้อย่างเชี่ยวชาญ
แม้การจับกุมครั้งใหญ่ในปี 2017 จะทำให้ขบวนการปลอมแปลงน้ำมันมะกอกในบางส่วนถูกทำลายลง แต่เครือข่ายอาชญากรรมที่เหลือยังคงดำเนินกิจกรรมนี้อยู่ในระดับที่น่ากังวล ผู้บริโภคในหลายประเทศยังคงต้องเผชิญกับผลิตภัณฑ์น้ำมันมะกอกปลอมที่ออกมาจากเครือข่ายเหล่านี้ ซึ่งมักจะมาพร้อมกับความเสี่ยงต่อสุขภาพ เนื่องจากอาจมีการปนเปื้อนสารเคมีอันตรายและการขาดความโปร่งใสในกระบวนการผลิต
Cosa Nostra ยังคงเป็นกลุ่มอาชญากรรมที่มีอิทธิพลมากในซิซิลีและมักจะใช้กลยุทธ์ในการขยายอำนาจผ่านการควบคุมการค้าและอุตสาหกรรมที่มีกำไรสูง การผลิตน้ำมันมะกอกแท้ในซิซิลีเป็นธุรกิจที่มีมูลค่ามหาศาลและเป็นที่นิยมในตลาดทั่วโลก ดังนั้นกลุ่ม Cosa Nostra จึงไม่ได้เพียงแค่ควบคุมการผลิตน้ำมันมะกอกปลอมเท่านั้น แต่ยังควบคุมการขนส่งและการกระจายสินค้าเหล่านี้ไปยังหลายประเทศที่ต้องการผลิตภัณฑ์ปลอมในราคาถูก
กลุ่ม Cosa Nostra ใช้ระบบ “pizzo” หรือการเก็บค่าคุ้มครองจากโรงงานผลิตน้ำมันมะกอกที่ไม่สามารถหลบหนีจากการเรียกเก็บเงินจากพวกเขาได้ รวมถึงการบังคับให้เจ้าของโรงงานผลิตน้ำมันมะกอกต้องซื้อวัตถุดิบที่ไม่ใช่มะกอกจากแหล่งที่พวกเขาควบคุม บางครั้งก็ร่วมมือกับกลุ่มอาชญากรในต่างประเทศ เพื่อให้สามารถขยายตลาดน้ำมันมะกอกปลอมในระดับนานาชาติได้
ขณะที่ Cosa Nostra ครองตลาดในซิซิลี นั้นทางกลุ่ม ’Ndrangheta มีบทบาทในแคว้นคาลาเบรียและมีอิทธิพลในการขยายกิจกรรมการผลิตน้ำมันมะกอกปลอมไปยังตลาดในยุโรปและทั่วโลก โดยเฉพาะในกลุ่มประเทศแถบยุโรปเหนือและอเมริกาเหนือ กลุ่มนี้เป็นหนึ่งในกลุ่มอาชญากรรมที่มีเครือข่ายการกระจายสินค้ามหาศาล รวมถึงน้ำมันมะกอกปลอมที่ไม่ได้รับการตรวจสอบจากผู้บริโภค
การกระจายสินค้าไม่ใช่แค่การจัดส่งน้ำมันมะกอกปลอมไปยังร้านค้าหรือผู้ขายที่ไม่ตรวจสอบ แต่ ‘Ndrangheta ยังมีบทบาทในการสร้างการเชื่อมต่อกับบริษัทส่งออกที่ดูเหมือนจะทำการค้าทั่วไป จนเมื่อการสอบสวนดำเนินไป ก็พบว่าเบื้องหลังของบริษัทเหล่านี้กลับเป็นการขนส่งน้ำมันมะกอกปลอมในปริมาณมหาศาล ขณะเดียวกันก็สร้างแรงกดดันต่อเจ้าหน้าที่และบรรดาผู้ที่พยายามจะเปิดเผยความจริง
ทั้งสองกลุ่มไม่ได้แยกกันไปตามแต่ละเขตแดน แต่พวกเขามักจะร่วมมือกันในการขยายเครือข่ายและหลีกเลี่ยงการถูกจับกุม การรวมตัวระหว่าง Cosa Nostra และ ’Ndrangheta ทำให้เกิดการรวมตัวของอำนาจและความรู้ในการหลบเลี่ยงการตรวจสอบจากเจ้าหน้าที่ ซึ่งทำให้การติดตามและจับกุมยากขึ้น ทั้งนี้เพราะพวกเขามักจะใช้วิธีการที่ซับซ้อนในการบังคับใช้การควบคุมตลาดน้ำมันมะกอกปลอม ซึ่งบางครั้งพวกเขาจะสร้างบริษัทหน้ากากและจดทะเบียนในประเทศที่ไม่มีกฎหมายควบคุมการตรวจสอบอาหารอย่างเคร่งครัด
ทั้ง Cosa Nostra และ ’Ndrangheta จึงเป็นหัวเรือใหญ่ที่ยังคงดำเนินกิจกรรมอาชญากรรมเหล่านี้อยู่ แม้จะมีการจับกุมและเปิดเผยเครือข่ายในบางส่วน แต่เครือข่ายการผลิตน้ำมันมะกอกปลอมยังคงมีความลับอยู่ในที่มืด และอิทธิพลของทั้งสองกลุ่มนี้ก็ยังคงสะท้อนอยู่ในอุตสาหกรรมอาหารทั่วโลก
แม้ว่าจะมีการจับกุมกลุ่มผู้ต้องหาหลายคนในช่วงการบุกค้นครั้งใหญ่ เจ้าหน้าที่ยังคงต้องทำงานหนักเพื่อขยายขอบเขตของการสืบสวน และทำลายเครือข่ายการกระจายสินค้าในระดับนานาชาติที่ทั้งสองกลุ่มควบคุมอยู่อย่างลับๆ แต่ในที่สุดแล้ว การพยายามทำลายอำนาจของ Cosa Nostra และ ’Ndrangheta ในวงการน้ำมันมะกอกปลอมยังคงเป็นการต่อสู้ที่ยาวนานและไม่สิ้นสุดอยู่ดีครับ
หนึ่งในปัญหาที่ผู้บริโภคต้องเผชิญคือ ความยากในการตรวจสอบคุณภาพของน้ำมันมะกอกที่ซื้อมา เนื่องจากการตรวจสอบเบื้องต้นเช่นการแช่ตู้เย็นเพื่อดูการแข็งตัวอาจไม่เพียงพอในการแยกแยะน้ำมันมะกอกแท้กับน้ำมันปลอมที่ผ่านการดัดแปลงด้วยสารเติมแต่งใหม่ ๆ เทคนิคการผลิตที่ซับซ้อนนี้ทำให้ผู้บริโภคต้องพึ่งพาแหล่งข้อมูลที่เชื่อถือได้และการรับรองจากหน่วยงานที่มีอำนาจ
แม้ในปัจจุบันหน่วยงานตำรวจและหน่วยงานกำกับดูแลในยุโรปและสหรัฐอเมริกาจะได้เพิ่มความเข้มงวดในการตรวจสอบและจับกุมขบวนการน้ำมันมะกอกปลอม แต่เครือข่ายขนาดใหญ่ที่มีความลับและการจัดการทางการเงินที่ซับซ้อนยังคงหลบหนีจากการปราบปรามอยู่เป็นอย่างดี ภาพรวมที่พบคือ ผู้ผลิตน้ำมันมะกอกปลอมที่ยังเหลืออยู่ในตลาดมักจะมีการเปลี่ยนแปลงสูตรและเทคนิคอย่างต่อเนื่อง เพื่อให้สามารถหลีกเลี่ยงการตรวจสอบจากห้องปฏิบัติการและการสอบสวนในระดับนานาชาติ
แล้วการจับกุมครั้งใหญ่ในปี 2017 ก็ส่งผลให้เกิดการปรับปรุงมาตรการตรวจสอบในอุตสาหกรรมอาหารและการบังคับใช้กฎหมายในยุโรป แต่ความท้าทายในการจับกุมและทำลายเครือข่ายขนาดใหญ่นี้ยังคงอยู่ เนื่องจากความร่วมมือระหว่างกลุ่มอาชญากรรมทั้งในอิตาลีและต่างประเทศมีความซับซ้อนและเป็นระบบที่ยากต่อการแตกสลาย
ในที่สุด เรื่องราวของการจับกุมขบวนการน้ำมันมะกอกปลอมในยุคนี้จึงเป็นเครื่องเตือนใจให้กับทั้งหน่วยงานกำกับดูแลและผู้บริโภคว่า การตรวจสอบคุณภาพและความโปร่งใสในอุตสาหกรรมอาหารเป็นสิ่งที่ไม่สามารถละเลยได้ และการจับกุมผู้กระทำผิดเพียงส่วนหนึ่งก็ยังไม่เพียงพอที่จะทำให้เครือข่ายอาชญากรรมที่มีอิทธิพลเหล่านี้ถูกทำลายหมดสิ้น ผู้บริโภคจึงควรเลือกซื้อผลิตภัณฑ์จากแหล่งที่เชื่อถือได้และมีการรับรองคุณภาพอย่างเคร่งครัด เพื่อป้องกันไม่ให้ตกเป็นเหยื่อของการหลอกลวงที่อาจมีผลกระทบต่อสุขภาพในระยะยาว
และการเรียนรู้ในการเลือกซื้อก็เป็นเกราะป้องกันขั้นต้นที่สำคัญ ถ้าจะบอกว่าหายาก บ้านเราไม่ค่อยมี เอาแบบง่ายๆในห้างก็ได้มั๊ง
ผมคงบอกได้แค่ เอาตามสะดวกพี่เลยครับ
ผมแค่สื่อสารสุขภาพเออร์ คนนึง
pirateketo
ฉลาก3รู้
ม้วนหางสิลูก #กูต้องรู้มั๊ย #siamstr
-
 @ 16d11430:61640947
2025-01-21 20:40:22
@ 16d11430:61640947
2025-01-21 20:40:22In a world drowning in Monopoly money, where people celebrate government-mandated inflation as "economic growth," it takes a special kind of clarity—nay, cynicism—to rise above the fiat circus. This is your guide to shedding your fiat f**ks and embracing the serene chaos of sound money, all while laughing at the absurdity of a world gone fiat-mad.
- Don’t Feed the Clowns
You know the clowns I’m talking about: central bankers in their tailored suits and smug smirks, wielding "tools" like interest rates and quantitative easing. Their tools are as real as a magician's wand, conjuring trillions of dollars out of thin air to keep their Ponzi economy afloat.
Rule #1: Don’t engage. If a clown offers you a hot take about the "strength of the dollar," smile, nod, and silently wonder how many cups of coffee their paycheck buys this month. Spoiler: fewer than last month.
- Turn Off the Fiat News
Do you really need another breathless headline about the next trillion-dollar deficit? Or the latest clickbait on why you should care about the stock market's emotional rollercoaster? Mainstream media exists to distract you, to keep you tethered to their illusion of importance.
Turn it off. Replace it with something sound, like the Bitcoin whitepaper. Or Nietzsche. At least Nietzsche knew we were doomed.
- Mock Their Inflationary Gospel
Fiat apologists will tell you that inflation is "necessary" and that 2% a year is a "healthy target." Sure, because a little robbery every year keeps society functioning, right? Ask them this: "If 2% is healthy, why not 20%? Why not 200%? Why not Venezuela?"
Fiat logic is like a bad acid trip: entertaining at first, but it quickly spirals into existential horror.
- Celebrate the Fiat Freakshow
Sometimes, the best way to resist the fiat clown show is to revel in its absurdity. Watch politicians print money like teenagers running up a credit card bill at Hot Topic, then watch the economists applaud it as "stimulus." It’s performance art, really. Andy Warhol could never.
- Build in the Chaos
While the fiat world burns, Bitcoiners build. This is the ultimate "not giving a fiat f**k" move: creating a parallel economy, one satoshi at a time. Run your Lightning node, stack sats, and laugh as the fiat circus consumes itself in a flaming pile of its own debt.
Let them argue about who gets to rearrange the deck chairs on the Titanic. You’re busy designing lifeboats.
- Adopt a Fiat-Free Lifestyle
Fiat-free living means minimizing your entanglement with their clown currency. Buy meat, not ETFs. Trade skills, not IOUs. Tip your barber in Bitcoin and ask if your landlord accepts Lightning. If they say no, chuckle and say, “You’ll learn soon enough.”
Every satoshi spent in the real economy is a slap in the face to the fiat overlords.
- Find the Humor in Collapse
Here’s the thing: the fiat system is unsustainable. You know it, I know it, even the clowns know it. The whole charade is destined to collapse under its own weight. When it does, find solace in the absurdity of it all.
Imagine the central bankers explaining hyperinflation to the public: "Turns out we can't print infinity after all." Pure comedy gold.
- Stay Ruthlessly Optimistic
Despite the doom and gloom, there’s hope. Bitcoin is hope. It’s the lifeboat for humanity, the cheat code to escape the fiat matrix. Cynicism doesn’t mean nihilism; it means seeing the rot for what it is and choosing to build something better.
So, don’t just reject the fiat clown show—replace it. Create a world where money is sound, transactions are sovereign, and wealth is measured in energy, not debt.
Final Thought: Burn the Tent Down
Aldous Huxley once envisioned a dystopia where people are so distracted by their own hedonistic consumption that they don’t realize they’re enslaved. Sound familiar? The fiat clown show is Brave New World on steroids, a spectacle designed to keep you pacified while your wealth evaporates.
But here’s the punchline: they can only enslave you if you care. By rejecting their system, you strip them of their power. So let them juggle their debts, inflate their bubbles, and print their trillions. You’ve got Bitcoin, and Bitcoin doesn’t give a fiat f**k.
Welcome to the satirical resistance. Now go stack some sats.
-
 @ 6830c409:ff17c655
2025-03-24 02:46:10
@ 6830c409:ff17c655
2025-03-24 02:46:10Nostr ഉപയോഗിച്ച് ഒരു ഉപയോക്താവായി നിങ്ങൾക്ക് ചെയ്യാൻ കഴിയുന്ന കാര്യങ്ങൾ:
-
കുറിപ്പുകൾ (Notes) പോസ്റ്റ് ചെയ്യുക: നിങ്ങളുടെ ചിന്തകൾ, അപ്ഡേറ്റുകൾ, അല്ലെങ്കിൽ മറ്റ് ഉള്ളടക്കങ്ങൾ പങ്കിടാൻ നിങ്ങൾക്ക് ചെറിയ സന്ദേശങ്ങൾ പോസ്റ്റ് ചെയ്യാം. ഈ നോട്ടുകൾക്ക് മാക്സിമം ലെങ്ത് എന്ന ലിമിറ്റ് ഇല്ല.
-
ദീർഘമായ കുറിപ്പുകൾ (Long-form Notes) പ്രസിദ്ധീകരിക്കുക: Nostr ദീർഘമായ ഉള്ളടക്കവും പിന്തുണയ്ക്കുന്നു, അതുവഴി നിങ്ങൾക്ക് ലേഖനങ്ങൾ, പ്രബന്ധങ്ങൾ, അല്ലെങ്കിൽ വിശദമായ പോസ്റ്റുകൾ എഴുതാനും പങ്കിടാനും കഴിയും.
-
Zapping (മൈക്രോ-പേയ്മെന്റുകൾ) ഉപയോഗിക്കുക: Nostr ലെ ലൈറ്റ്നിംഗ് നെറ്റ്വർക്ക് ഉപയോഗിച്ച്, നിങ്ങൾക്ക് ചെറിയ തുകകൾ (സാറ്റോഷികൾ) അയയ്ക്കാൻ കഴിയും, ഇത് കണ്ടൻ്റ് ക്രിയേറ്റർമാർക്ക് പിന്തുണ നൽകാൻ സഹായിക്കുന്നു. സറ്റോഷി എന്നത് ബിറ്റ്കോയിൻ നാണയത്തിന്റെ ഏറ്റവും ചെറിയ യൂണിറ്റാണ്.
-
ചാറ്റുകൾ (Chats) ഉപയോഗിക്കുക: മറ്റ് ഉപയോക്താക്കളുമായി സ്വകാര്യമായി അല്ലെങ്കിൽ പബ്ലിക്ക് ചാറ്റ് റൂമുകളിൽ ആശയവിനിമയം നടത്താൻ നിങ്ങൾക്ക് Nostr ലെ ചാറ്റ് ഫീച്ചറുകൾ ഉപയോഗിക്കാം. ഈ ചാറ്റുകൾ എൻക്രിപ്റ്റ് ചെയ്തതും സുരക്ഷിതവുമാണ്, അതിനാൽ നിങ്ങളുടെ സംഭാഷണങ്ങൾ സ്വകാര്യത ഉറപ്പാക്കുന്നു.
-
മാർക്കറ്റ്പ്ലേസുകൾ (Marketplaces) ഉപയോഗിക്കുക: Nostr മാർക്കറ്റ്പ്ലേസുകൾ ഉപയോഗിച്ച്, ഉപയോക്താക്കൾക്ക് പീർ-ടു-പീർ അടിസ്ഥാനത്തിൽ വസ്തുക്കളും സേവനങ്ങളും വാങ്ങാനും വിൽക്കാനും കഴിയും.
-
വ്യത്യസ്ത ക്ലയന്റുകൾ പരീക്ഷിക്കുക: Nostr വിവിധ ക്ലയന്റുകൾ ഉപയോഗിച്ച് പ്രവർത്തിക്കുന്നു. ഓരോ ക്ലയന്റിനും വ്യത്യസ്ത സവിശേഷതകളും ഇന്റർഫേസുകളും ഉണ്ട്, അതിനാൽ നിങ്ങളുടെ ഇഷ്ടാനുസരണം തിരഞ്ഞെടുക്കാം. Damus, Amethyst, Iris, Yakihonne, Primal, NoStrudel തുടങ്ങിയവയാണ് ചില പ്രശസ്ത ക്ലയന്റുകൾ.
-
മറ്റ് ഉപയോക്താക്കളെ പിന്തുടരുക: Nostr ലെ നിങ്ങളുടെ പ്രൊഫൈൽ ഉപയോഗിച്ച്, നിങ്ങൾക്ക് മറ്റ് ഉപയോക്താക്കളെ പിന്തുടരാനും അവരുടെ പോസ്റ്റുകളുമായി ഇടപെടാനും കഴിയും. ആർട്ടിഫിഷ്യലായി നോട്ടുകളെ ബൂസ്റ്റ് ചെയ്യാൻ കഴിയില്ല - അതുകൊണ്ടു തന്നെ, വളരെ സ്വാഭാവികമായ ഒരു ടൈമ്ലൈൻ ആകും എല്ലാവർക്കും ലഭിക്കുക.
-
മീഡിയയും ഫയലുകളും പങ്കിടുക: നിങ്ങളുടെ ഫോളോവേഴ്സുമായി ചിത്രങ്ങൾ, വീഡിയോകൾ, മറ്റ് ഫയലുകൾ എന്നിവ പങ്കിടുക, ഇത് നിങ്ങളുടെ പോസ്റ്റുകൾ കൂടുതൽ ആകർഷകമാക്കുന്നു.
-
പോളുകളിലും സർവേയുകളിലും പങ്കെടുക്കുക: Nostr ലെ പോളുകളിലും സർവേയുകളിലും പങ്കെടുക്കുക, ഇത് സമൂഹത്തിന്റെ അഭിപ്രായങ്ങൾ അറിയാനും ചർച്ചകളിൽ പങ്കെടുക്കാനും സഹായിക്കുന്നു.
-
യാക്കിഹോൺ പോലുള്ള ക്ലയൻ്റുകളിൽ പോസ്റ്റുകൾക്ക് ടെമ്പ്ലേറ്റ് ഉണ്ടാക്കാനും അത് ഷെയർ ചെയ്യാനും ഒക്കെ സാധിക്കും. ഇത് കൂടുതൽ ഇൻ്ററാക്ടീവ് അനുഭവം നൽകുന്നു, പ്രത്യേകിച്ച് നിങ്ങളുടെ പോസ്റ്റുകൾക്ക് ഒരു യുണീക്ക് ലുക്ക് ആൻഡ് ഫീൽ നൽകാൻ സാധിക്കും.
ഓക്കെ. നിങ്ങൾ എപ്പൊഴാണ് Nostr ഉപയോഗിക്കാൻ തുടങ്ങുന്നത്? നിങ്ങളുടെ നൊസ്റ്റർ ഐഡി/പബ്ലിക്ക് കീ ഷെയർ ചെയ്യൂ.
-
-
 @ 9e69e420:d12360c2
2025-01-21 19:31:48
@ 9e69e420:d12360c2
2025-01-21 19:31:48Oregano oil is a potent natural compound that offers numerous scientifically-supported health benefits.
Active Compounds
The oil's therapeutic properties stem from its key bioactive components: - Carvacrol and thymol (primary active compounds) - Polyphenols and other antioxidant
Antimicrobial Properties
Bacterial Protection The oil demonstrates powerful antibacterial effects, even against antibiotic-resistant strains like MRSA and other harmful bacteria. Studies show it effectively inactivates various pathogenic bacteria without developing resistance.
Antifungal Effects It effectively combats fungal infections, particularly Candida-related conditions like oral thrush, athlete's foot, and nail infections.
Digestive Health Benefits
Oregano oil supports digestive wellness by: - Promoting gastric juice secretion and enzyme production - Helping treat Small Intestinal Bacterial Overgrowth (SIBO) - Managing digestive discomfort, bloating, and IBS symptoms
Anti-inflammatory and Antioxidant Effects
The oil provides significant protective benefits through: - Powerful antioxidant activity that fights free radicals - Reduction of inflammatory markers in the body - Protection against oxidative stress-related conditions
Respiratory Support
It aids respiratory health by: - Loosening mucus and phlegm - Suppressing coughs and throat irritation - Supporting overall respiratory tract function
Additional Benefits
Skin Health - Improves conditions like psoriasis, acne, and eczema - Supports wound healing through antibacterial action - Provides anti-aging benefits through antioxidant properties
Cardiovascular Health Studies show oregano oil may help: - Reduce LDL (bad) cholesterol levels - Support overall heart health
Pain Management The oil demonstrates effectiveness in: - Reducing inflammation-related pain - Managing muscle discomfort - Providing topical pain relief
Safety Note
While oregano oil is generally safe, it's highly concentrated and should be properly diluted before use Consult a healthcare provider before starting supplementation, especially if taking other medications.
-
 @ b17fccdf:b7211155
2025-01-21 17:02:21
@ b17fccdf:b7211155
2025-01-21 17:02:21The past 26 August, Tor introduced officially a proof-of-work (PoW) defense for onion services designed to prioritize verified network traffic as a deterrent against denial of service (DoS) attacks.
~ > This feature at the moment, is deactivate by default, so you need to follow these steps to activate this on a MiniBolt node:
- Make sure you have the latest version of Tor installed, at the time of writing this post, which is v0.4.8.6. Check your current version by typing
tor --versionExample of expected output:
Tor version 0.4.8.6. This build of Tor is covered by the GNU General Public License (https://www.gnu.org/licenses/gpl-3.0.en.html) Tor is running on Linux with Libevent 2.1.12-stable, OpenSSL 3.0.9, Zlib 1.2.13, Liblzma 5.4.1, Libzstd N/A and Glibc 2.36 as libc. Tor compiled with GCC version 12.2.0~ > If you have v0.4.8.X, you are OK, if not, type
sudo apt update && sudo apt upgradeand confirm to update.- Basic PoW support can be checked by running this command:
tor --list-modulesExpected output:
relay: yes dirauth: yes dircache: yes pow: **yes**~ > If you have
pow: yes, you are OK- Now go to the torrc file of your MiniBolt and add the parameter to enable PoW for each hidden service added
sudo nano /etc/tor/torrcExample:
```
Hidden Service BTC RPC Explorer
HiddenServiceDir /var/lib/tor/hidden_service_btcrpcexplorer/ HiddenServiceVersion 3 HiddenServicePoWDefensesEnabled 1 HiddenServicePort 80 127.0.0.1:3002 ```
~ > Bitcoin Core and LND use the Tor control port to automatically create the hidden service, requiring no action from the user. We have submitted a feature request in the official GitHub repositories to explore the need for the integration of Tor's PoW defense into the automatic creation process of the hidden service. You can follow them at the following links:
- Bitcoin Core: https://github.com/lightningnetwork/lnd/issues/8002
- LND: https://github.com/bitcoin/bitcoin/issues/28499
More info:
- https://blog.torproject.org/introducing-proof-of-work-defense-for-onion-services/
- https://gitlab.torproject.org/tpo/onion-services/onion-support/-/wikis/Documentation/PoW-FAQ
Enjoy it MiniBolter! 💙
-
 @ 6be5cc06:5259daf0
2025-01-21 01:51:46
@ 6be5cc06:5259daf0
2025-01-21 01:51:46Bitcoin: Um sistema de dinheiro eletrônico direto entre pessoas.
Satoshi Nakamoto
satoshin@gmx.com
www.bitcoin.org
Resumo
O Bitcoin é uma forma de dinheiro digital que permite pagamentos diretos entre pessoas, sem a necessidade de um banco ou instituição financeira. Ele resolve um problema chamado gasto duplo, que ocorre quando alguém tenta gastar o mesmo dinheiro duas vezes. Para evitar isso, o Bitcoin usa uma rede descentralizada onde todos trabalham juntos para verificar e registrar as transações.
As transações são registradas em um livro público chamado blockchain, protegido por uma técnica chamada Prova de Trabalho. Essa técnica cria uma cadeia de registros que não pode ser alterada sem refazer todo o trabalho já feito. Essa cadeia é mantida pelos computadores que participam da rede, e a mais longa é considerada a verdadeira.
Enquanto a maior parte do poder computacional da rede for controlada por participantes honestos, o sistema continuará funcionando de forma segura. A rede é flexível, permitindo que qualquer pessoa entre ou saia a qualquer momento, sempre confiando na cadeia mais longa como prova do que aconteceu.
1. Introdução
Hoje, quase todos os pagamentos feitos pela internet dependem de bancos ou empresas como processadores de pagamento (cartões de crédito, por exemplo) para funcionar. Embora esse sistema seja útil, ele tem problemas importantes porque é baseado em confiança.
Primeiro, essas empresas podem reverter pagamentos, o que é útil em caso de erros, mas cria custos e incertezas. Isso faz com que pequenas transações, como pagar centavos por um serviço, se tornem inviáveis. Além disso, os comerciantes são obrigados a desconfiar dos clientes, pedindo informações extras e aceitando fraudes como algo inevitável.
Esses problemas não existem no dinheiro físico, como o papel-moeda, onde o pagamento é final e direto entre as partes. No entanto, não temos como enviar dinheiro físico pela internet sem depender de um intermediário confiável.
O que precisamos é de um sistema de pagamento eletrônico baseado em provas matemáticas, não em confiança. Esse sistema permitiria que qualquer pessoa enviasse dinheiro diretamente para outra, sem depender de bancos ou processadores de pagamento. Além disso, as transações seriam irreversíveis, protegendo vendedores contra fraudes, mas mantendo a possibilidade de soluções para disputas legítimas.
Neste documento, apresentamos o Bitcoin, que resolve o problema do gasto duplo usando uma rede descentralizada. Essa rede cria um registro público e protegido por cálculos matemáticos, que garante a ordem das transações. Enquanto a maior parte da rede for controlada por pessoas honestas, o sistema será seguro contra ataques.
2. Transações
Para entender como funciona o Bitcoin, é importante saber como as transações são realizadas. Imagine que você quer transferir uma "moeda digital" para outra pessoa. No sistema do Bitcoin, essa "moeda" é representada por uma sequência de registros que mostram quem é o atual dono. Para transferi-la, você adiciona um novo registro comprovando que agora ela pertence ao próximo dono. Esse registro é protegido por um tipo especial de assinatura digital.
O que é uma assinatura digital?
Uma assinatura digital é como uma senha secreta, mas muito mais segura. No Bitcoin, cada usuário tem duas chaves: uma "chave privada", que é secreta e serve para criar a assinatura, e uma "chave pública", que pode ser compartilhada com todos e é usada para verificar se a assinatura é válida. Quando você transfere uma moeda, usa sua chave privada para assinar a transação, provando que você é o dono. A próxima pessoa pode usar sua chave pública para confirmar isso.
Como funciona na prática?
Cada "moeda" no Bitcoin é, na verdade, uma cadeia de assinaturas digitais. Vamos imaginar o seguinte cenário:
- A moeda está com o Dono 0 (você). Para transferi-la ao Dono 1, você assina digitalmente a transação com sua chave privada. Essa assinatura inclui o código da transação anterior (chamado de "hash") e a chave pública do Dono 1.
- Quando o Dono 1 quiser transferir a moeda ao Dono 2, ele assinará a transação seguinte com sua própria chave privada, incluindo também o hash da transação anterior e a chave pública do Dono 2.
- Esse processo continua, formando uma "cadeia" de transações. Qualquer pessoa pode verificar essa cadeia para confirmar quem é o atual dono da moeda.
Resolvendo o problema do gasto duplo
Um grande desafio com moedas digitais é o "gasto duplo", que é quando uma mesma moeda é usada em mais de uma transação. Para evitar isso, muitos sistemas antigos dependiam de uma entidade central confiável, como uma casa da moeda, que verificava todas as transações. No entanto, isso criava um ponto único de falha e centralizava o controle do dinheiro.
O Bitcoin resolve esse problema de forma inovadora: ele usa uma rede descentralizada onde todos os participantes (os "nós") têm acesso a um registro completo de todas as transações. Cada nó verifica se as transações são válidas e se a moeda não foi gasta duas vezes. Quando a maioria dos nós concorda com a validade de uma transação, ela é registrada permanentemente na blockchain.
Por que isso é importante?
Essa solução elimina a necessidade de confiar em uma única entidade para gerenciar o dinheiro, permitindo que qualquer pessoa no mundo use o Bitcoin sem precisar de permissão de terceiros. Além disso, ela garante que o sistema seja seguro e resistente a fraudes.
3. Servidor Timestamp
Para assegurar que as transações sejam realizadas de forma segura e transparente, o sistema Bitcoin utiliza algo chamado de "servidor de registro de tempo" (timestamp). Esse servidor funciona como um registro público que organiza as transações em uma ordem específica.
Ele faz isso agrupando várias transações em blocos e criando um código único chamado "hash". Esse hash é como uma impressão digital que representa todo o conteúdo do bloco. O hash de cada bloco é amplamente divulgado, como se fosse publicado em um jornal ou em um fórum público.
Esse processo garante que cada bloco de transações tenha um registro de quando foi criado e que ele existia naquele momento. Além disso, cada novo bloco criado contém o hash do bloco anterior, formando uma cadeia contínua de blocos conectados — conhecida como blockchain.
Com isso, se alguém tentar alterar qualquer informação em um bloco anterior, o hash desse bloco mudará e não corresponderá ao hash armazenado no bloco seguinte. Essa característica torna a cadeia muito segura, pois qualquer tentativa de fraude seria imediatamente detectada.
O sistema de timestamps é essencial para provar a ordem cronológica das transações e garantir que cada uma delas seja única e autêntica. Dessa forma, ele reforça a segurança e a confiança na rede Bitcoin.
4. Prova-de-Trabalho
Para implementar o registro de tempo distribuído no sistema Bitcoin, utilizamos um mecanismo chamado prova-de-trabalho. Esse sistema é semelhante ao Hashcash, desenvolvido por Adam Back, e baseia-se na criação de um código único, o "hash", por meio de um processo computacionalmente exigente.
A prova-de-trabalho envolve encontrar um valor especial que, quando processado junto com as informações do bloco, gere um hash que comece com uma quantidade específica de zeros. Esse valor especial é chamado de "nonce". Encontrar o nonce correto exige um esforço significativo do computador, porque envolve tentativas repetidas até que a condição seja satisfeita.
Esse processo é importante porque torna extremamente difícil alterar qualquer informação registrada em um bloco. Se alguém tentar mudar algo em um bloco, seria necessário refazer o trabalho de computação não apenas para aquele bloco, mas também para todos os blocos que vêm depois dele. Isso garante a segurança e a imutabilidade da blockchain.
A prova-de-trabalho também resolve o problema de decidir qual cadeia de blocos é a válida quando há múltiplas cadeias competindo. A decisão é feita pela cadeia mais longa, pois ela representa o maior esforço computacional já realizado. Isso impede que qualquer indivíduo ou grupo controle a rede, desde que a maioria do poder de processamento seja mantida por participantes honestos.
Para garantir que o sistema permaneça eficiente e equilibrado, a dificuldade da prova-de-trabalho é ajustada automaticamente ao longo do tempo. Se novos blocos estiverem sendo gerados rapidamente, a dificuldade aumenta; se estiverem sendo gerados muito lentamente, a dificuldade diminui. Esse ajuste assegura que novos blocos sejam criados aproximadamente a cada 10 minutos, mantendo o sistema estável e funcional.
5. Rede
A rede Bitcoin é o coração do sistema e funciona de maneira distribuída, conectando vários participantes (ou nós) para garantir o registro e a validação das transações. Os passos para operar essa rede são:
-
Transmissão de Transações: Quando alguém realiza uma nova transação, ela é enviada para todos os nós da rede. Isso é feito para garantir que todos estejam cientes da operação e possam validá-la.
-
Coleta de Transações em Blocos: Cada nó agrupa as novas transações recebidas em um "bloco". Este bloco será preparado para ser adicionado à cadeia de blocos (a blockchain).
-
Prova-de-Trabalho: Os nós competem para resolver a prova-de-trabalho do bloco, utilizando poder computacional para encontrar um hash válido. Esse processo é como resolver um quebra-cabeça matemático difícil.
-
Envio do Bloco Resolvido: Quando um nó encontra a solução para o bloco (a prova-de-trabalho), ele compartilha esse bloco com todos os outros nós na rede.
-
Validação do Bloco: Cada nó verifica o bloco recebido para garantir que todas as transações nele contidas sejam válidas e que nenhuma moeda tenha sido gasta duas vezes. Apenas blocos válidos são aceitos.
-
Construção do Próximo Bloco: Os nós que aceitaram o bloco começam a trabalhar na criação do próximo bloco, utilizando o hash do bloco aceito como base (hash anterior). Isso mantém a continuidade da cadeia.
Resolução de Conflitos e Escolha da Cadeia Mais Longa
Os nós sempre priorizam a cadeia mais longa, pois ela representa o maior esforço computacional já realizado, garantindo maior segurança. Se dois blocos diferentes forem compartilhados simultaneamente, os nós trabalharão no primeiro bloco recebido, mas guardarão o outro como uma alternativa. Caso o segundo bloco eventualmente forme uma cadeia mais longa (ou seja, tenha mais blocos subsequentes), os nós mudarão para essa nova cadeia.
Tolerância a Falhas
A rede é robusta e pode lidar com mensagens que não chegam a todos os nós. Uma transação não precisa alcançar todos os nós de imediato; basta que chegue a um número suficiente deles para ser incluída em um bloco. Da mesma forma, se um nó não receber um bloco em tempo hábil, ele pode solicitá-lo ao perceber que está faltando quando o próximo bloco é recebido.
Esse mecanismo descentralizado permite que a rede Bitcoin funcione de maneira segura, confiável e resiliente, sem depender de uma autoridade central.
6. Incentivo
O incentivo é um dos pilares fundamentais que sustenta o funcionamento da rede Bitcoin, garantindo que os participantes (nós) continuem operando de forma honesta e contribuindo com recursos computacionais. Ele é estruturado em duas partes principais: a recompensa por mineração e as taxas de transação.
Recompensa por Mineração
Por convenção, o primeiro registro em cada bloco é uma transação especial que cria novas moedas e as atribui ao criador do bloco. Essa recompensa incentiva os mineradores a dedicarem poder computacional para apoiar a rede. Como não há uma autoridade central para emitir moedas, essa é a maneira pela qual novas moedas entram em circulação. Esse processo pode ser comparado ao trabalho de garimpeiros, que utilizam recursos para colocar mais ouro em circulação. No caso do Bitcoin, o "recurso" consiste no tempo de CPU e na energia elétrica consumida para resolver a prova-de-trabalho.
Taxas de Transação
Além da recompensa por mineração, os mineradores também podem ser incentivados pelas taxas de transação. Se uma transação utiliza menos valor de saída do que o valor de entrada, a diferença é tratada como uma taxa, que é adicionada à recompensa do bloco contendo essa transação. Com o passar do tempo e à medida que o número de moedas em circulação atinge o limite predeterminado, essas taxas de transação se tornam a principal fonte de incentivo, substituindo gradualmente a emissão de novas moedas. Isso permite que o sistema opere sem inflação, uma vez que o número total de moedas permanece fixo.
Incentivo à Honestidade
O design do incentivo também busca garantir que os participantes da rede mantenham um comportamento honesto. Para um atacante que consiga reunir mais poder computacional do que o restante da rede, ele enfrentaria duas escolhas:
- Usar esse poder para fraudar o sistema, como reverter transações e roubar pagamentos.
- Seguir as regras do sistema, criando novos blocos e recebendo recompensas legítimas.
A lógica econômica favorece a segunda opção, pois um comportamento desonesto prejudicaria a confiança no sistema, diminuindo o valor de todas as moedas, incluindo aquelas que o próprio atacante possui. Jogar dentro das regras não apenas maximiza o retorno financeiro, mas também preserva a validade e a integridade do sistema.
Esse mecanismo garante que os incentivos econômicos estejam alinhados com o objetivo de manter a rede segura, descentralizada e funcional ao longo do tempo.
7. Recuperação do Espaço em Disco
Depois que uma moeda passa a estar protegida por muitos blocos na cadeia, as informações sobre as transações antigas que a geraram podem ser descartadas para economizar espaço em disco. Para que isso seja possível sem comprometer a segurança, as transações são organizadas em uma estrutura chamada "árvore de Merkle". Essa árvore funciona como um resumo das transações: em vez de armazenar todas elas, guarda apenas um "hash raiz", que é como uma assinatura compacta que representa todo o grupo de transações.
Os blocos antigos podem, então, ser simplificados, removendo as partes desnecessárias dessa árvore. Apenas a raiz do hash precisa ser mantida no cabeçalho do bloco, garantindo que a integridade dos dados seja preservada, mesmo que detalhes específicos sejam descartados.
Para exemplificar: imagine que você tenha vários recibos de compra. Em vez de guardar todos os recibos, você cria um documento e lista apenas o valor total de cada um. Mesmo que os recibos originais sejam descartados, ainda é possível verificar a soma com base nos valores armazenados.
Além disso, o espaço ocupado pelos blocos em si é muito pequeno. Cada bloco sem transações ocupa apenas cerca de 80 bytes. Isso significa que, mesmo com blocos sendo gerados a cada 10 minutos, o crescimento anual em espaço necessário é insignificante: apenas 4,2 MB por ano. Com a capacidade de armazenamento dos computadores crescendo a cada ano, esse espaço continuará sendo trivial, garantindo que a rede possa operar de forma eficiente sem problemas de armazenamento, mesmo a longo prazo.
8. Verificação de Pagamento Simplificada
É possível confirmar pagamentos sem a necessidade de operar um nó completo da rede. Para isso, o usuário precisa apenas de uma cópia dos cabeçalhos dos blocos da cadeia mais longa (ou seja, a cadeia com maior esforço de trabalho acumulado). Ele pode verificar a validade de uma transação ao consultar os nós da rede até obter a confirmação de que tem a cadeia mais longa. Para isso, utiliza-se o ramo Merkle, que conecta a transação ao bloco em que ela foi registrada.
Entretanto, o método simplificado possui limitações: ele não pode confirmar uma transação isoladamente, mas sim assegurar que ela ocupa um lugar específico na cadeia mais longa. Dessa forma, se um nó da rede aprova a transação, os blocos subsequentes reforçam essa aceitação.
A verificação simplificada é confiável enquanto a maioria dos nós da rede for honesta. Contudo, ela se torna vulnerável caso a rede seja dominada por um invasor. Nesse cenário, um atacante poderia fabricar transações fraudulentas que enganariam o usuário temporariamente até que o invasor obtivesse controle completo da rede.
Uma estratégia para mitigar esse risco é configurar alertas nos softwares de nós completos. Esses alertas identificam blocos inválidos, sugerindo ao usuário baixar o bloco completo para confirmar qualquer inconsistência. Para maior segurança, empresas que realizam pagamentos frequentes podem preferir operar seus próprios nós, reduzindo riscos e permitindo uma verificação mais direta e confiável.
9. Combinando e Dividindo Valor
No sistema Bitcoin, cada unidade de valor é tratada como uma "moeda" individual, mas gerenciar cada centavo como uma transação separada seria impraticável. Para resolver isso, o Bitcoin permite que valores sejam combinados ou divididos em transações, facilitando pagamentos de qualquer valor.
Entradas e Saídas
Cada transação no Bitcoin é composta por:
- Entradas: Representam os valores recebidos em transações anteriores.
- Saídas: Correspondem aos valores enviados, divididos entre os destinatários e, eventualmente, o troco para o remetente.
Normalmente, uma transação contém:
- Uma única entrada com valor suficiente para cobrir o pagamento.
- Ou várias entradas combinadas para atingir o valor necessário.
O valor total das saídas nunca excede o das entradas, e a diferença (se houver) pode ser retornada ao remetente como troco.
Exemplo Prático
Imagine que você tem duas entradas:
- 0,03 BTC
- 0,07 BTC
Se deseja enviar 0,08 BTC para alguém, a transação terá:
- Entrada: As duas entradas combinadas (0,03 + 0,07 BTC = 0,10 BTC).
- Saídas: Uma para o destinatário (0,08 BTC) e outra como troco para você (0,02 BTC).
Essa flexibilidade permite que o sistema funcione sem precisar manipular cada unidade mínima individualmente.
Difusão e Simplificação
A difusão de transações, onde uma depende de várias anteriores e assim por diante, não representa um problema. Não é necessário armazenar ou verificar o histórico completo de uma transação para utilizá-la, já que o registro na blockchain garante sua integridade.
10. Privacidade
O modelo bancário tradicional oferece um certo nível de privacidade, limitando o acesso às informações financeiras apenas às partes envolvidas e a um terceiro confiável (como bancos ou instituições financeiras). No entanto, o Bitcoin opera de forma diferente, pois todas as transações são publicamente registradas na blockchain. Apesar disso, a privacidade pode ser mantida utilizando chaves públicas anônimas, que desvinculam diretamente as transações das identidades das partes envolvidas.
Fluxo de Informação
- No modelo tradicional, as transações passam por um terceiro confiável que conhece tanto o remetente quanto o destinatário.
- No Bitcoin, as transações são anunciadas publicamente, mas sem revelar diretamente as identidades das partes. Isso é comparável a dados divulgados por bolsas de valores, onde informações como o tempo e o tamanho das negociações (a "fita") são públicas, mas as identidades das partes não.
Protegendo a Privacidade
Para aumentar a privacidade no Bitcoin, são adotadas as seguintes práticas:
- Chaves Públicas Anônimas: Cada transação utiliza um par de chaves diferentes, dificultando a associação com um proprietário único.
- Prevenção de Ligação: Ao usar chaves novas para cada transação, reduz-se a possibilidade de links evidentes entre múltiplas transações realizadas pelo mesmo usuário.
Riscos de Ligação
Embora a privacidade seja fortalecida, alguns riscos permanecem:
- Transações multi-entrada podem revelar que todas as entradas pertencem ao mesmo proprietário, caso sejam necessárias para somar o valor total.
- O proprietário da chave pode ser identificado indiretamente por transações anteriores que estejam conectadas.
11. Cálculos
Imagine que temos um sistema onde as pessoas (ou computadores) competem para adicionar informações novas (blocos) a um grande registro público (a cadeia de blocos ou blockchain). Este registro é como um livro contábil compartilhado, onde todos podem verificar o que está escrito.
Agora, vamos pensar em um cenário: um atacante quer enganar o sistema. Ele quer mudar informações já registradas para beneficiar a si mesmo, por exemplo, desfazendo um pagamento que já fez. Para isso, ele precisa criar uma versão alternativa do livro contábil (a cadeia de blocos dele) e convencer todos os outros participantes de que essa versão é a verdadeira.
Mas isso é extremamente difícil.
Como o Ataque Funciona
Quando um novo bloco é adicionado à cadeia, ele depende de cálculos complexos que levam tempo e esforço. Esses cálculos são como um grande quebra-cabeça que precisa ser resolvido.
- Os “bons jogadores” (nós honestos) estão sempre trabalhando juntos para resolver esses quebra-cabeças e adicionar novos blocos à cadeia verdadeira.
- O atacante, por outro lado, precisa resolver quebra-cabeças sozinho, tentando “alcançar” a cadeia honesta para que sua versão alternativa pareça válida.
Se a cadeia honesta já está vários blocos à frente, o atacante começa em desvantagem, e o sistema está projetado para que a dificuldade de alcançá-los aumente rapidamente.
A Corrida Entre Cadeias
Você pode imaginar isso como uma corrida. A cada bloco novo que os jogadores honestos adicionam à cadeia verdadeira, eles se distanciam mais do atacante. Para vencer, o atacante teria que resolver os quebra-cabeças mais rápido que todos os outros jogadores honestos juntos.
Suponha que:
- A rede honesta tem 80% do poder computacional (ou seja, resolve 8 de cada 10 quebra-cabeças).
- O atacante tem 20% do poder computacional (ou seja, resolve 2 de cada 10 quebra-cabeças).
Cada vez que a rede honesta adiciona um bloco, o atacante tem que "correr atrás" e resolver mais quebra-cabeças para alcançar.
Por Que o Ataque Fica Cada Vez Mais Improvável?
Vamos usar uma fórmula simples para mostrar como as chances de sucesso do atacante diminuem conforme ele precisa "alcançar" mais blocos:
P = (q/p)^z
- q é o poder computacional do atacante (20%, ou 0,2).
- p é o poder computacional da rede honesta (80%, ou 0,8).
- z é a diferença de blocos entre a cadeia honesta e a cadeia do atacante.
Se o atacante está 5 blocos atrás (z = 5):
P = (0,2 / 0,8)^5 = (0,25)^5 = 0,00098, (ou, 0,098%)
Isso significa que o atacante tem menos de 0,1% de chance de sucesso — ou seja, é muito improvável.
Se ele estiver 10 blocos atrás (z = 10):
P = (0,2 / 0,8)^10 = (0,25)^10 = 0,000000095, (ou, 0,0000095%).
Neste caso, as chances de sucesso são praticamente nulas.
Um Exemplo Simples
Se você jogar uma moeda, a chance de cair “cara” é de 50%. Mas se precisar de 10 caras seguidas, sua chance já é bem menor. Se precisar de 20 caras seguidas, é quase impossível.
No caso do Bitcoin, o atacante precisa de muito mais do que 20 caras seguidas. Ele precisa resolver quebra-cabeças extremamente difíceis e alcançar os jogadores honestos que estão sempre à frente. Isso faz com que o ataque seja inviável na prática.
Por Que Tudo Isso é Seguro?
- A probabilidade de sucesso do atacante diminui exponencialmente. Isso significa que, quanto mais tempo passa, menor é a chance de ele conseguir enganar o sistema.
- A cadeia verdadeira (honesta) está protegida pela força da rede. Cada novo bloco que os jogadores honestos adicionam à cadeia torna mais difícil para o atacante alcançar.
E Se o Atacante Tentar Continuar?
O atacante poderia continuar tentando indefinidamente, mas ele estaria gastando muito tempo e energia sem conseguir nada. Enquanto isso, os jogadores honestos estão sempre adicionando novos blocos, tornando o trabalho do atacante ainda mais inútil.
Assim, o sistema garante que a cadeia verdadeira seja extremamente segura e que ataques sejam, na prática, impossíveis de ter sucesso.
12. Conclusão
Propusemos um sistema de transações eletrônicas que elimina a necessidade de confiança, baseando-se em assinaturas digitais e em uma rede peer-to-peer que utiliza prova de trabalho. Isso resolve o problema do gasto duplo, criando um histórico público de transações imutável, desde que a maioria do poder computacional permaneça sob controle dos participantes honestos. A rede funciona de forma simples e descentralizada, com nós independentes que não precisam de identificação ou coordenação direta. Eles entram e saem livremente, aceitando a cadeia de prova de trabalho como registro do que ocorreu durante sua ausência. As decisões são tomadas por meio do poder de CPU, validando blocos legítimos, estendendo a cadeia e rejeitando os inválidos. Com este mecanismo de consenso, todas as regras e incentivos necessários para o funcionamento seguro e eficiente do sistema são garantidos.
Faça o download do whitepaper original em português: https://bitcoin.org/files/bitcoin-paper/bitcoin_pt_br.pdf
-
 @ 4d4fb5ff:1e821f47
2025-03-24 02:03:53
@ 4d4fb5ff:1e821f47
2025-03-24 02:03:53The entire genetic sequence for peptidase E (pepE, e. coli). Genes in living organisms are subject to mutation across time. In contrast, information on the bitcoin ledger is immutable. By etching the pepE DNA sequence onto bitcoin, its ability to evolve is lost. This challenges the significance of genetic information in a foreign digital context. I chose to keep the title “PEPEGENE” in upper case as a homage to the naming convention for Counterparty assets. This additionally contrasts the notation of a digital asset identifier (PEPEGENE) against the notation of biological identifiers (a,t,c or g), which are kept in lower case.
-
 @ 9d92077c:38d27146
2025-01-20 20:46:31
@ 9d92077c:38d27146
2025-01-20 20:46:31Like King Arthur pulling the sword Excalibur from the stone to reclaim his rightful place as king, the Excalibur system empowers Nostr users to recover control of their digital identities and networks from malicious infiltrators. This proposal introduces a robust framework for key recovery and re-association, ensuring that users can seamlessly regain control of their accounts while preserving their social connections, metadata, and event history. In an age where security and trust are paramount, Excalibur offers a practical and resilient solution to one of the most pressing challenges in decentralized networks.
—-
The Importance of Key Recovery on Nostr
One of Nostr’s greatest strengths is its reliance on public and private key pairs to establish identities and ensure message authenticity. However, the simplicity of this cryptographic model comes with a significant vulnerability: key compromise. If a user’s private key is lost or stolen, they face catastrophic consequences: * Loss of Identity: The user cannot post, interact, or manage their profile. * Disruption of Social Graph: Followers and contacts lose their connection to the user. * Trust Erosion: An attacker controlling the compromised key can impersonate the user, damaging their reputation.
While decentralization is a core principle of Nostr, the lack of a built-in recovery mechanism undermines long-term usability and user confidence. Excalibur addresses this gap with an innovative system for recovering compromised keys and maintaining social continuity.
—-
Proposed Solution: The Excalibur System
The Excalibur system introduces a primary key and secure backup key model to Nostr, enabling users to recover their accounts and re-associate events in the event of key compromise. This system relies on a combination of cryptographic proofs, event indexing, and client/relay cooperation to ensure a seamless and secure transition.
1. Primary and Secure Keys
Users establish a primary key for everyday activity and a secure backup key stored offline. The primary key broadcasts an association with the secure key using a
set_secure_keyevent.2. Key Transition Event
Upon detecting a compromise, the user activates the secure key by publishing a
key_transitionevent.This event includes: * The compromised primary key. * The new secure key. * A cryptographic proof linking the two. * A timestamp and optional metadata.
3. Social Graph Transition
Clients automatically replace the compromised key with the secure key in follow lists, contact lists, and other social data.
Followers are notified of the transition and encouraged to follow the secure key.
4. Unified Identity View
Historical events remain immutable but are re-indexed by relays to associate with the secure key for continuity.
Clients display a unified profile view, differentiating old and new events.
5. Seamless Transition for Existing Accounts
Existing Nostr users can integrate Excalibur by broadcasting a set_secure_key event linking their current primary key to a secure backup key. While historical events and metadata associated with the primary key remain unchanged, all new events after activation of the secure key are seamlessly associated with the updated identity. Clients should provide user-friendly tools to guide existing users through this setup process.
6. Endless Security Chain
Once a secure key is activated and becomes the new primary key, users must set up a new secure backup key immediately by broadcasting a new
set_secure_keyevent.This ensures an endless chain of security, preventing future compromises from leaving users vulnerable.
Clients should include UX enhancements such as prompts, reminders, and automated tools to help users maintain their security chain efficiently.
7. Insurance Model for Relays
Users pay an upfront premium to relays for re-association services, ensuring resources are available for recovery operations.
Clients act as brokers, aggregating multiple relay insurance contracts into a single, user-friendly offering. They manage user payments, distribute premiums to participating relays, and earn a commission for their services.
This brokerage model incentivizes clients to participate actively in the Excalibur system and ensures broader adoption across the network.
—-
Implementation Framework
Cryptographic Foundations
- The secure key must be pre-announced and linked to the primary key using a signed
set_secure_keyevent. - During key transition, the key_transition event includes a signature proving the association.
Relay Behavior
- Relays index the key_transition event and re-link historical data to the secure key.
- Events from the old key are tagged as "deprecated" but remain accessible.
Client Behavior
- Clients validate the
key_transitionevent and update social graphs automatically. - Followers are notified and prompted to follow the secure key.
- Profiles display both old and new events under a unified identity.
- Clients implement features to facilitate existing users' onboarding and provide tools to manage the security chain seamlessly.
—-
Benefits of Excalibur
Resilience: Users can recover from key compromise without losing their digital identity or network.
Trust: The cryptographic proofs ensure the legitimacy of key transitions, preserving trust in the system.
Sustainability: The insurance premium model incentivizes relay adoption and ensures fair resource allocation.
User-Friendly: Automated transitions reduce the complexity for end users, making Nostr more accessible.
Adaptability: Existing accounts can benefit from Excalibur without disruption, ensuring broad applicability.
—-
Call to Action
The Excalibur system is a vital enhancement to the Nostr protocol, addressing the critical issue of key recovery while maintaining decentralization and user sovereignty. By adopting Excalibur, we can strengthen the network’s resilience, foster trust, and ensure that users retain control of their identities in an ever-evolving digital landscape. We invite the Nostr community to collaborate on refining and implementing this proposal, turning the vision of Excalibur into a reality.
Together, let’s ensure that no user is ever left powerless in the face of compromise. Let’s reclaim the sword and secure the kingdom.
- The secure key must be pre-announced and linked to the primary key using a signed