-
 @ daa41bed:88f54153
2025-02-09 16:50:04
@ daa41bed:88f54153
2025-02-09 16:50:04There has been a good bit of discussion on Nostr over the past few days about the merits of zaps as a method of engaging with notes, so after writing a rather lengthy article on the pros of a strategic Bitcoin reserve, I wanted to take some time to chime in on the much more fun topic of digital engagement.
Let's begin by defining a couple of things:
Nostr is a decentralized, censorship-resistance protocol whose current biggest use case is social media (think Twitter/X). Instead of relying on company servers, it relies on relays that anyone can spin up and own their own content. Its use cases are much bigger, though, and this article is hosted on my own relay, using my own Nostr relay as an example.
Zap is a tip or donation denominated in sats (small units of Bitcoin) sent from one user to another. This is generally done directly over the Lightning Network but is increasingly using Cashu tokens. For the sake of this discussion, how you transmit/receive zaps will be irrelevant, so don't worry if you don't know what Lightning or Cashu are.
If we look at how users engage with posts and follows/followers on platforms like Twitter, Facebook, etc., it becomes evident that traditional social media thrives on engagement farming. The more outrageous a post, the more likely it will get a reaction. We see a version of this on more visual social platforms like YouTube and TikTok that use carefully crafted thumbnail images to grab the user's attention to click the video. If you'd like to dive deep into the psychology and science behind social media engagement, let me know, and I'd be happy to follow up with another article.
In this user engagement model, a user is given the option to comment or like the original post, or share it among their followers to increase its signal. They receive no value from engaging with the content aside from the dopamine hit of the original experience or having their comment liked back by whatever influencer they provide value to. Ad revenue flows to the content creator. Clout flows to the content creator. Sales revenue from merch and content placement flows to the content creator. We call this a linear economy -- the idea that resources get created, used up, then thrown away. Users create content and farm as much engagement as possible, then the content is forgotten within a few hours as they move on to the next piece of content to be farmed.
What if there were a simple way to give value back to those who engage with your content? By implementing some value-for-value model -- a circular economy. Enter zaps.

Unlike traditional social media platforms, Nostr does not actively use algorithms to determine what content is popular, nor does it push content created for active user engagement to the top of a user's timeline. Yes, there are "trending" and "most zapped" timelines that users can choose to use as their default, but these use relatively straightforward engagement metrics to rank posts for these timelines.
That is not to say that we may not see clients actively seeking to refine timeline algorithms for specific metrics. Still, the beauty of having an open protocol with media that is controlled solely by its users is that users who begin to see their timeline gamed towards specific algorithms can choose to move to another client, and for those who are more tech-savvy, they can opt to run their own relays or create their own clients with personalized algorithms and web of trust scoring systems.
Zaps enable the means to create a new type of social media economy in which creators can earn for creating content and users can earn by actively engaging with it. Like and reposting content is relatively frictionless and costs nothing but a simple button tap. Zaps provide active engagement because they signal to your followers and those of the content creator that this post has genuine value, quite literally in the form of money—sats.

I have seen some comments on Nostr claiming that removing likes and reactions is for wealthy people who can afford to send zaps and that the majority of people in the US and around the world do not have the time or money to zap because they have better things to spend their money like feeding their families and paying their bills. While at face value, these may seem like valid arguments, they, unfortunately, represent the brainwashed, defeatist attitude that our current economic (and, by extension, social media) systems aim to instill in all of us to continue extracting value from our lives.
Imagine now, if those people dedicating their own time (time = money) to mine pity points on social media would instead spend that time with genuine value creation by posting content that is meaningful to cultural discussions. Imagine if, instead of complaining that their posts get no zaps and going on a tirade about how much of a victim they are, they would empower themselves to take control of their content and give value back to the world; where would that leave us? How much value could be created on a nascent platform such as Nostr, and how quickly could it overtake other platforms?
Other users argue about user experience and that additional friction (i.e., zaps) leads to lower engagement, as proven by decades of studies on user interaction. While the added friction may turn some users away, does that necessarily provide less value? I argue quite the opposite. You haven't made a few sats from zaps with your content? Can't afford to send some sats to a wallet for zapping? How about using the most excellent available resource and spending 10 seconds of your time to leave a comment? Likes and reactions are valueless transactions. Social media's real value derives from providing monetary compensation and actively engaging in a conversation with posts you find interesting or thought-provoking. Remember when humans thrived on conversation and discussion for entertainment instead of simply being an onlooker of someone else's life?
If you've made it this far, my only request is this: try only zapping and commenting as a method of engagement for two weeks. Sure, you may end up liking a post here and there, but be more mindful of how you interact with the world and break yourself from blind instinct. You'll thank me later.

-
 @ dc4cd086:cee77c06
2025-02-09 03:35:25
@ dc4cd086:cee77c06
2025-02-09 03:35:25Have you ever wanted to learn from lengthy educational videos but found it challenging to navigate through hours of content? Our new tool addresses this problem by transforming long-form video lectures into easily digestible, searchable content.
Key Features:
Video Processing:
- Automatically downloads YouTube videos, transcripts, and chapter information
- Splits transcripts into sections based on video chapters
Content Summarization:
- Utilizes language models to transform spoken content into clear, readable text
- Formats output in AsciiDoc for improved readability and navigation
- Highlights key terms and concepts with [[term]] notation for potential cross-referencing
Diagram Extraction:
- Analyzes video entropy to identify static diagram/slide sections
- Provides a user-friendly GUI for manual selection of relevant time ranges
- Allows users to pick representative frames from selected ranges
Going Forward:
Currently undergoing a rewrite to improve organization and functionality, but you are welcome to try the current version, though it might not work on every machine. Will support multiple open and closed language models for user choice Free and open-source, allowing for personal customization and integration with various knowledge bases. Just because we might not have it on our official Alexandria knowledge base, you are still welcome to use it on you own personal or community knowledge bases! We want to help find connections between ideas that exist across relays, allowing individuals and groups to mix and match knowledge bases between each other, allowing for any degree of openness you care.
While designed with #Alexandria users in mind, it's available for anyone to use and adapt to their own learning needs.
Screenshots
Frame Selection

This is a screenshot of the frame selection interface. You'll see a signal that represents frame entropy over time. The vertical lines indicate the start and end of a chapter. Within these chapters you can select the frames by clicking and dragging the mouse over the desired range where you think diagram is in that chapter. At the bottom is an option that tells the program to select a specific number of frames from that selection.
Diagram Extraction

This is a screenshot of the diagram extraction interface. For every selection you've made, there will be a set of frames that you can choose from. You can select and deselect as many frames as you'd like to save.
Links
- repo: https://github.com/limina1/video_article_converter
- Nostr Apps 101: https://www.youtube.com/watch?v=Flxa_jkErqE
Output
And now, we have a demonstration of the final result of this tool, with some quick cleaning up. The video we will be using this tool on is titled Nostr Apps 101 by nostr:npub1nxy4qpqnld6kmpphjykvx2lqwvxmuxluddwjamm4nc29ds3elyzsm5avr7 during Nostrasia. The following thread is an analog to the modular articles we are constructing for Alexandria, and I hope it conveys the functionality we want to create in the knowledge space. Note, this tool is the first step! You could use a different prompt that is most appropriate for the specific context of the transcript you are working with, but you can also manually clean up any discrepancies that don't portray the video accurately. You can now view the article on #Alexandria https://next-alexandria.gitcitadel.eu/publication?d=nostr-apps-101
Initially published as chained kind 1's nostr:nevent1qvzqqqqqqypzp5r5hd579v2sszvvzfel677c8dxgxm3skl773sujlsuft64c44ncqy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgwwaehxw309ahx7uewd3hkctcpzemhxue69uhhyetvv9ujumt0wd68ytnsw43z7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qgewaehxw309aex2mrp0yh8xmn0wf6zuum0vd5kzmp0qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgc7hglpn
Or view on Coracle https://coracle.social /nevent1qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgcppemhxue69uhkummn9ekx7mp0qgsdqa9md83tz5yqnrqjw07hhkpmfjpkuv9hlh5v8yhu8z274w9dv7qnnq0s3
-
 @ 16d11430:61640947
2025-02-09 00:12:22
@ 16d11430:61640947
2025-02-09 00:12:22Introduction: The Power of Focused Attention
In an age of distraction, power is not merely held through material wealth, authority, or control over others—it is built through focused attention. The human brain, a complex quantum-biological processor, constructs reality through perception. When harnessed correctly, focused attention allows individuals to transcend limitations, reshape their reality, and live free.
Power, then, is not external—it is a construct supported by the mind and created within the brain. Understanding how this works offers a path to transcendence, autonomy, and liberation from imposed limitations.
The Neuroscience of Focused Attention: Constructing Reality
The brain is a prediction engine, constantly processing information and filtering out irrelevant stimuli. Focused attention directs this process, acting as a spotlight that selects what becomes part of one's conscious experience. This is the fundamental mechanism behind cognitive power.
- Neuroplasticity: Building Power Through Repetition
The brain adapts to repeated stimuli through neuroplasticity. What one focuses on consistently rewires neural pathways, strengthening certain thoughts, beliefs, and abilities. Over time, this focus builds an internal structure of power—a network of ideas and perceptions that define one’s reality.
If one focuses on problems, they grow.
If one focuses on solutions, they appear.
If one focuses on fear, it shapes perception.
If one focuses on mastery, skills develop.
- The Quantum Mind: Attention as a Creative Force
Quantum physics suggests that observation influences reality. Just as subatomic particles behave differently when measured, focused attention may act as a force that shapes possibilities into tangible outcomes.
This aligns with the ancient concept that "energy flows where attention goes." What one attends to with intention can manifest as action, opportunity, and ultimately, freedom.
- The Reticular Activating System (RAS): Filtering Reality
The Reticular Activating System (RAS) in the brainstem acts as a gatekeeper for focus. It determines what information enters conscious awareness. When trained, it can filter out distractions and amplify pathways toward a desired goal.
Want to see opportunities? Program the RAS by setting clear intentions.
Want to break free from limiting beliefs? Train focus away from conditioned fears.
The Mind’s Role: Transcending Limitations
The mind is the interpreter of the brain’s electrical and biochemical activity. While the brain processes raw data, the mind provides meaning. This distinction is crucial because meaning determines how one experiences reality.
- Breaking Mental Chains: Rewriting Narratives
Most limitations are narratives—stories imposed by culture, society, or personal history. True power lies in rewriting these stories.
Instead of “I am trapped by my circumstances,” shift to “I create my own reality.”
Instead of “I need permission,” shift to “I give myself permission.”
By restructuring meaning, the mind can redefine the limits of what is possible.
- The Silence Paradox: Accessing Higher States
Silence, both literal and mental, creates space for higher-order thinking. Just as quantum tunneling allows subatomic particles to pass through barriers without energy loss, silence allows the mind to bypass noise and access deeper intelligence.
Meditation, stillness, and solitude amplify internal power.
The ability to not react is a form of control over external influence.
True mastery comes from detachment—engaging the world without being controlled by it.
Transcendence: Living Free Through Mental Autonomy
To transcend means to rise above imposed structures—whether societal, psychological, or energetic. The construct of power built through focused attention allows one to escape control mechanisms and live autonomously.
- Sovereignty of Mind: Owning One’s Thoughts
A free mind is one that chooses its inputs rather than being programmed by external forces. This requires:
Awareness of mental conditioning (social narratives, propaganda, biases)
Intentional thought selection (curating what enters the mental space)
Guarding attention fiercely (not allowing distraction to hijack focus)
- Detachment From Control Structures
Society operates on the principle of attention capture—through media, politics, and algorithms that direct thought patterns. Escaping these requires detachment.
Do not react emotionally to fear-based programming.
Cultivate independent thought by questioning imposed narratives.
Reduce external noise to amplify internal wisdom.
- The Flow State: Moving Beyond Constraints
When focus is refined to its highest degree, one enters flow state—a condition where action and awareness merge, and limitations dissolve.
In flow, work becomes effortless.
Creativity becomes boundless.
Freedom becomes not just a philosophy, but a lived experience.
Conclusion: The Mind as the Ultimate Key to Freedom
Power is not an external possession—it is the ability to direct one’s own focus. Through the interplay of brain function, cognitive attention, and mental discipline, one constructs personal sovereignty. The individual who masters focus, controls reality.
Freedom is not given. It is built—through attention, intention, and an unwavering commitment to mental autonomy.
-
 @ 6cc4225f:942b7222
2024-12-30 00:32:47
@ 6cc4225f:942b7222
2024-12-30 00:32:47(Cover image photo credit: The Crypto Times)
“Our world of widows needs to be saved / it’s now or never — victim or victory, rebel or regret / who you are and who you claim to be / no more heroes.” -Converge, “No Heroes”
Usually, bad takes from big figures in the Bitcoin space roll off my back. I often don’t feel a need to counter them because 1.) Everyone is entitled to their opinion and 2.) I don’t enjoy spending my time arguing with people on the Internet.
But when a take is really bad — downright evil — I feel compelled to respond.
And respond I did to a bad take this week (link in just a second, first some context).
Lately in the media, MicroStrategy Chair Michael Saylor has been laying out his vision for a digital asset framework.
This framework includes conceptualizing Bitcoin as a commodity — nothing more than capital — and stablecoins like Tether (USDT) and USD Coin (USDC) as “digital currencies” (his words).
As if someone who considers themselves a “triple bitcoin maxi” (maybe one of the lamest terms ever) denying that bitcoin is a currency weren’t nauseating enough, his “evil genius plan” (his words) to get the world hooked on USD stablecoins as money while the US hoards bitcoin should have you upchuck everything in your guts if you truly believe in Bitcoin’s value proposition.
Below (a few lines down) is the piece I wrote countering Saylor’s perspective.
If there are two things I hope you take away from it, the first is to KILL YOUR IDOLS (not literally, of course) and the second is that WE ARE BITCOIN, and if we believe in the technology — all dimensions of it — we have to defend it.
Enjoy.
Michael Saylor Doesn't Understand Bitcoin
## Support The Open Dialogue Foundation
Speaking of defending Bitcoin, we all owe a debt of gratitude to the work that the Open Dialogue Foundation (ODF) is doing to defend our legal right to use non-custodial bitcoin wallets.
Please read the following piece I wrote this week to learn more.
Protect Your Non-Custodial Bitcoin Wallet — Support The Open Dialogue Foundation
And please make a tax-deductible contribution (before the year’s end) to the organization here.
Bitcoin’s Second Book-Length Academic Text — The Satoshi Papers — Coming Soon
This week, I published my interview with Natalie Smolenski, a PhD-holding theoretical anthropologist who often makes very valuable thought contributions to the Bitcoin space.
What I loved most about this interview (and I loved a lot about it) is Smolenski’s lack of reverence.
Two of my favorite quotes from the interview:
“There was kind of a triumph of a certain very statist approach to socialism and even communism in the American academy, in the Anglophone academy, that has persisted to this day, where there's, like I was saying earlier, a suspicion of anything smacking of individualism as bourgeois conceit or reinscribing social hierarchies, racial hierarchies, gender hierarchies, blah, blah, blah.”
The “blah, blah, blah” hit hard. It reminded me of how I used to tune out when speaking with a good portion of my co-workers during the years I taught at the college level.
The other one:
“What do you hope people will take away from The Satoshi Papers?
*> If there's only one idea that people take away from it, it's that your emancipation does not require the state. You do not need to wait for the government.
*> My God, take control of your life. You can, it is within your power to do so, and here are some examples of ways that people throughout human history have chosen to do so."
The “My God” was so properly placed. Chef’s kiss.
Check out to entire piece to absorb more of Smolenski’s wisdom.
Thank you all for reading, and here’s to a great week ahead!
Best,
Frank
-
 @ 3ffac3a6:2d656657
2025-02-06 03:58:47
@ 3ffac3a6:2d656657
2025-02-06 03:58:47Motivations
Recently, my sites hosted behind Cloudflare tunnels mysteriously stopped working—not once, but twice. The first outage occurred about a week ago. Interestingly, when I switched to using the 1.1.1.1 WARP VPN on my cellphone or PC, the sites became accessible again. Clearly, the issue wasn't with the sites themselves but something about the routing. This led me to the brilliant (or desperate) idea of routing all Cloudflare-bound traffic through a WARP tunnel in my local network.
Prerequisites
- A "server" with an amd64 processor (the WARP client only works on amd64 architecture). I'm using an old mac mini, but really, anything with an amd64 processor will do.
- Basic knowledge of Linux commands.
- Access to your Wi-Fi router's settings (if you plan to configure routes there).
Step 1: Installing the WARP CLI
- Update your system packages:
bash sudo apt update && sudo apt upgrade -y- Download and install the WARP CLI:
```bash curl https://pkg.cloudflareclient.com/pubkey.gpg | sudo gpg --yes --dearmor --output /usr/share/keyrings/cloudflare-warp-archive-keyring.gpg
echo "deb [arch=amd64 signed-by=/usr/share/keyrings/cloudflare-warp-archive-keyring.gpg] https://pkg.cloudflareclient.com/ $(lsb_release -cs) main" | sudo tee /etc/apt/sources.list.d/cloudflare-client.list
sudo apt-get update && sudo apt-get install cloudflare-warp ``` 3. Register and connect to WARP:
Run the following commands to register and connect to WARP:
```bash sudo warp-cli register sudo warp-cli connect ````
Confirm the connection with:
bash warp-cli status
Step 2: Routing Traffic on the Server Machine
Now that WARP is connected, let's route the local network's Cloudflare-bound traffic through this tunnel.
- Enable IP forwarding:
bash sudo sysctl -w net.ipv4.ip_forward=1Make it persistent after reboot:
bash echo 'net.ipv4.ip_forward=1' | sudo tee -a /etc/sysctl.conf sudo sysctl -p- Set up firewall rules to forward traffic:
bash sudo nft add rule ip filter FORWARD iif "eth0" oif "CloudflareWARP" ip saddr 192.168.31.0/24 ip daddr 104.0.0.0/8 accept sudo nft add rule ip filter FORWARD iif "CloudflareWARP" oif "eth0" ip saddr 104.0.0.0/8 ip daddr 192.168.31.0/24 ct state established,related acceptReplace
eth0with your actual network interface if different.- Make rules persistent:
bash sudo apt install nftables sudo nft list ruleset > /etc/nftables.conf
Step 3: Configuring the Route on a Local PC (Linux)
On your local Linux machine:
- Add a static route:
bash sudo ip route add 104.0.0.0/24 via <SERVER_IP>Replace
<SERVER_IP>with the internal IP of your WARP-enabled server. This should be a temporary solution, since it only effects a local machine. For a solution that can effect the whole local network, please see next step.
Step 4: Configuring the Route on Your Wi-Fi Router (Recommended)
If your router allows adding static routes:
- Log in to your router's admin interface.
- Navigate to the Static Routing section. (This may vary depending on the router model.)
- Add a new static route:
- Destination Network:
104.0.0.0 - Subnet Mask:
255.255.255.0 - Gateway:
<SERVER_IP> - Metric:
1(or leave it default) - Save and apply the settings.
One of the key advantages of this method is how easy it is to disable once your ISP's routing issues are resolved. Since the changes affect the entire network at once, you can quickly restore normal network behavior by simply removing the static routes or disabling the forwarding rules, all without the need for complex reconfigurations.
Final Thoughts
Congratulations! You've now routed all your Cloudflare-bound traffic through a secure WARP tunnel, effectively bypassing mysterious connectivity issues. If the sites ever go down again, at least you’ll have one less thing to blame—and one more thing to debug.
-
 @ e3ba5e1a:5e433365
2025-02-05 17:47:16
@ e3ba5e1a:5e433365
2025-02-05 17:47:16I got into a friendly discussion on X regarding health insurance. The specific question was how to deal with health insurance companies (presumably unfairly) denying claims? My answer, as usual: get government out of it!
The US healthcare system is essentially the worst of both worlds:
- Unlike full single payer, individuals incur high costs
- Unlike a true free market, regulation causes increases in costs and decreases competition among insurers
I'm firmly on the side of moving towards the free market. (And I say that as someone living under a single payer system now.) Here's what I would do:
- Get rid of tax incentives that make health insurance tied to your employer, giving individuals back proper freedom of choice.
- Reduce regulations significantly.
-
In the short term, some people will still get rejected claims and other obnoxious behavior from insurance companies. We address that in two ways:
- Due to reduced regulations, new insurance companies will be able to enter the market offering more reliable coverage and better rates, and people will flock to them because they have the freedom to make their own choices.
- Sue the asses off of companies that reject claims unfairly. And ideally, as one of the few legitimate roles of government in all this, institute new laws that limit the ability of fine print to allow insurers to escape their responsibilities. (I'm hesitant that the latter will happen due to the incestuous relationship between Congress/regulators and insurers, but I can hope.)
Will this magically fix everything overnight like politicians normally promise? No. But it will allow the market to return to a healthy state. And I don't think it will take long (order of magnitude: 5-10 years) for it to come together, but that's just speculation.
And since there's a high correlation between those who believe government can fix problems by taking more control and demanding that only credentialed experts weigh in on a topic (both points I strongly disagree with BTW): I'm a trained actuary and worked in the insurance industry, and have directly seen how government regulation reduces competition, raises prices, and harms consumers.
And my final point: I don't think any prior art would be a good comparison for deregulation in the US, it's such a different market than any other country in the world for so many reasons that lessons wouldn't really translate. Nonetheless, I asked Grok for some empirical data on this, and at best the results of deregulation could be called "mixed," but likely more accurately "uncertain, confused, and subject to whatever interpretation anyone wants to apply."
https://x.com/i/grok/share/Zc8yOdrN8lS275hXJ92uwq98M
-
 @ e3ba5e1a:5e433365
2025-02-04 08:29:42
@ e3ba5e1a:5e433365
2025-02-04 08:29:42President Trump has started rolling out his tariffs, something I blogged about in November. People are talking about these tariffs a lot right now, with many people (correctly) commenting on how consumers will end up with higher prices as a result of these tariffs. While that part is true, I’ve seen a lot of people taking it to the next, incorrect step: that consumers will pay the entirety of the tax. I put up a poll on X to see what people thought, and while the right answer got a lot of votes, it wasn't the winner.

For purposes of this blog post, our ultimate question will be the following:
- Suppose apples currently sell for $1 each in the entire United States.
- There are domestic sellers and foreign sellers of apples, all receiving the same price.
- There are no taxes or tariffs on the purchase of apples.
- The question is: if the US federal government puts a $0.50 import tariff per apple, what will be the change in the following:
- Number of apples bought in the US
- Price paid by buyers for apples in the US
- Post-tax price received by domestic apple producers
- Post-tax price received by foreign apple producers
Before we can answer that question, we need to ask an easier, first question: before instituting the tariff, why do apples cost $1?
And finally, before we dive into the details, let me provide you with the answers to the ultimate question. I recommend you try to guess these answers before reading this, and if you get it wrong, try to understand why:
- The number of apples bought will go down
- The buyers will pay more for each apple they buy, but not the full amount of the tariff
- Domestic apple sellers will receive a higher price per apple
- Foreign apple sellers will receive a lower price per apple, but not lowered by the full amount of the tariff
In other words, regardless of who sends the payment to the government, both taxed parties (domestic buyers and foreign sellers) will absorb some of the costs of the tariff, while domestic sellers will benefit from the protectionism provided by tariffs and be able to sell at a higher price per unit.
Marginal benefit
All of the numbers discussed below are part of a helper Google Sheet I put together for this analysis. Also, apologies about the jagged lines in the charts below, I hadn’t realized before starting on this that there are some difficulties with creating supply and demand charts in Google Sheets.
Let’s say I absolutely love apples, they’re my favorite food. How much would I be willing to pay for a single apple? You might say “$1, that’s the price in the supermarket,” and in many ways you’d be right. If I walk into supermarket A, see apples on sale for $50, and know that I can buy them at supermarket B for $1, I’ll almost certainly leave A and go buy at B.
But that’s not what I mean. What I mean is: how high would the price of apples have to go everywhere so that I’d no longer be willing to buy a single apple? This is a purely personal, subjective opinion. It’s impacted by how much money I have available, other expenses I need to cover, and how much I like apples. But let’s say the number is $5.
How much would I be willing to pay for another apple? Maybe another $5. But how much am I willing to pay for the 1,000th apple? 10,000th? At some point, I’ll get sick of apples, or run out of space to keep the apples, or not be able to eat, cook, and otherwise preserve all those apples before they rot.
The point being: I’ll be progressively willing to spend less and less money for each apple. This form of analysis is called marginal benefit: how much benefit (expressed as dollars I’m willing to spend) will I receive from each apple? This is a downward sloping function: for each additional apple I buy (quantity demanded), the price I’m willing to pay goes down. This is what gives my personal demand curve. And if we aggregate demand curves across all market participants (meaning: everyone interested in buying apples), we end up with something like this:
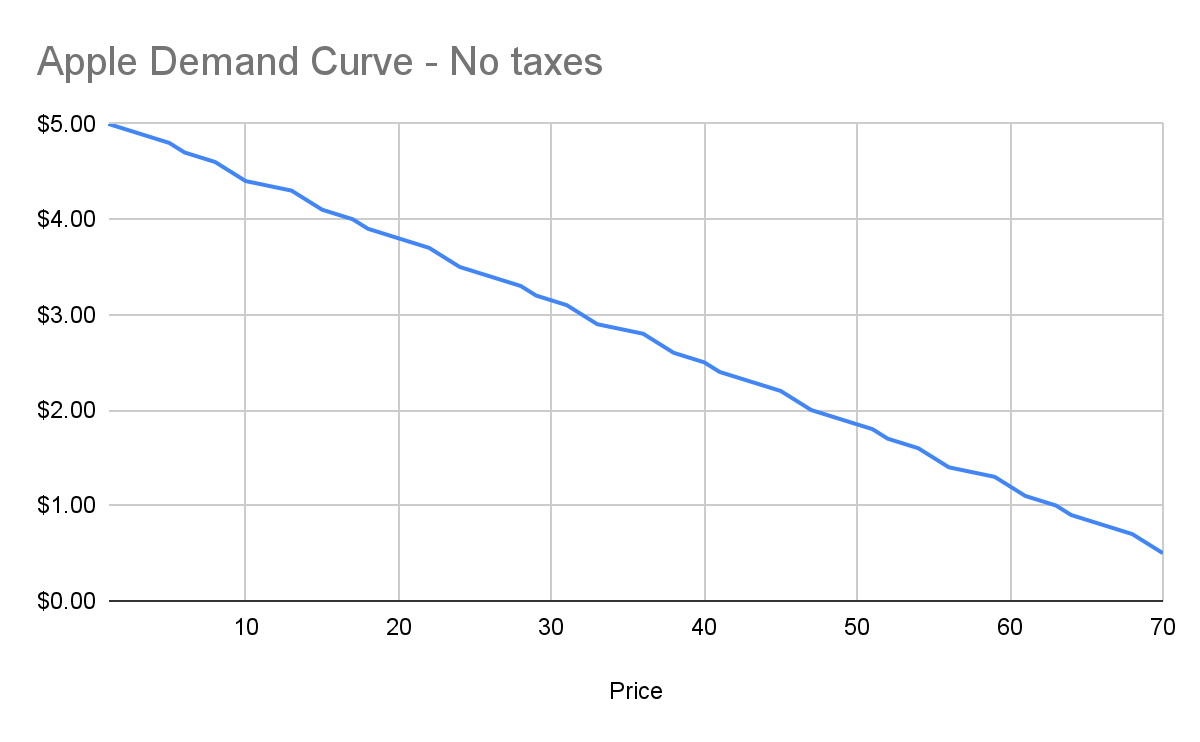
Assuming no changes in people’s behavior and other conditions in the market, this chart tells us how many apples will be purchased by our buyers at each price point between $0.50 and $5. And ceteris paribus (all else being equal), this will continue to be the demand curve for apples.
Marginal cost
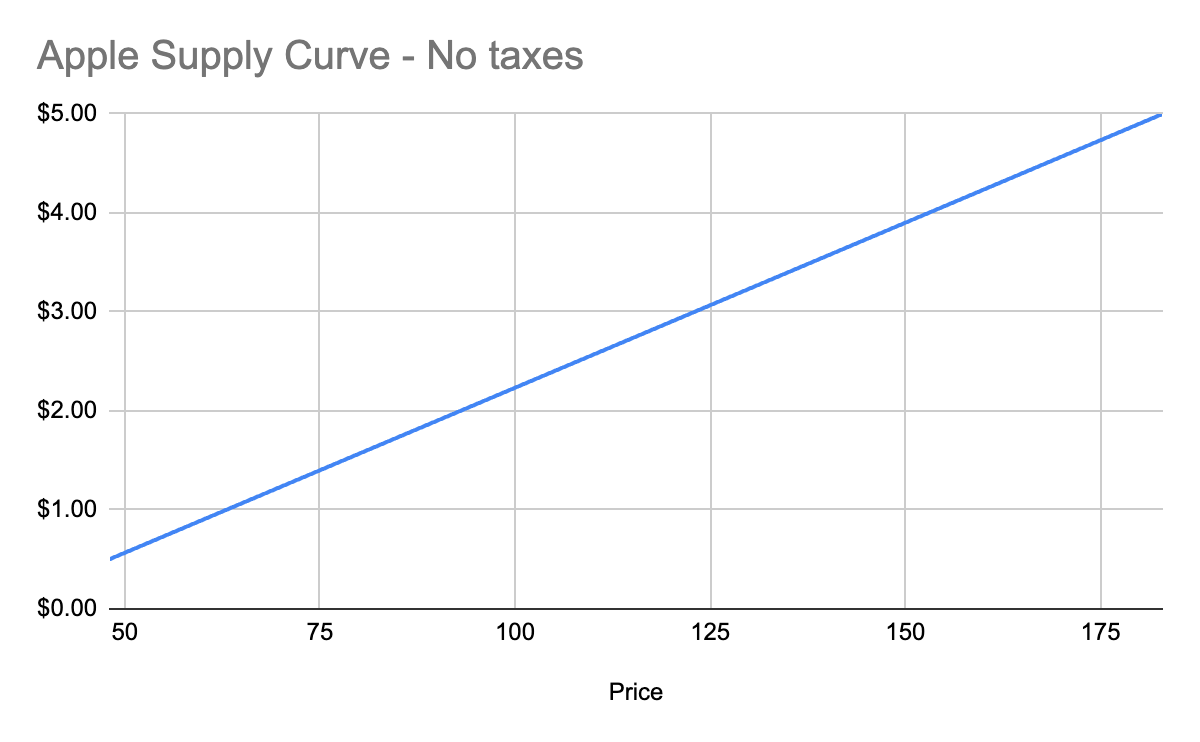
Demand is half the story of economics. The other half is supply, or: how many apples will I sell at each price point? Supply curves are upward sloping: the higher the price, the more a person or company is willing and able to sell a product.
Let’s understand why. Suppose I have an apple orchard. It’s a large property right next to my house. With about 2 minutes of effort, I can walk out of my house, find the nearest tree, pick 5 apples off the tree, and call it a day. 5 apples for 2 minutes of effort is pretty good, right?
Yes, there was all the effort necessary to buy the land, and plant the trees, and water them… and a bunch more than I likely can’t even guess at. We’re going to ignore all of that for our analysis, because for short-term supply-and-demand movement, we can ignore these kinds of sunk costs. One other simplification: in reality, supply curves often start descending before ascending. This accounts for achieving efficiencies of scale after the first number of units purchased. But since both these topics are unneeded for understanding taxes, I won’t go any further.
Anyway, back to my apple orchard. If someone offers me $0.50 per apple, I can do 2 minutes of effort and get $2.50 in revenue, which equates to a $75/hour wage for me. I’m more than happy to pick apples at that price!
However, let’s say someone comes to buy 10,000 apples from me instead. I no longer just walk out to my nearest tree. I’m going to need to get in my truck, drive around, spend the day in the sun, pay for gas, take a day off of my day job (let’s say it pays me $70/hour). The costs go up significantly. Let’s say it takes 5 days to harvest all those apples myself, it costs me $100 in fuel and other expenses, and I lose out on my $70/hour job for 5 days. We end up with:
- Total expenditure: $100 + $70 * 8 hours a day * 5 days \== $2900
- Total revenue: $5000 (10,000 apples at $0.50 each)
- Total profit: $2100
So I’m still willing to sell the apples at this price, but it’s not as attractive as before. And as the number of apples purchased goes up, my costs keep increasing. I’ll need to spend more money on fuel to travel more of my property. At some point I won’t be able to do the work myself anymore, so I’ll need to pay others to work on the farm, and they’ll be slower at picking apples than me (less familiar with the property, less direct motivation, etc.). The point being: at some point, the number of apples can go high enough that the $0.50 price point no longer makes me any money.
This kind of analysis is called marginal cost. It refers to the additional amount of expenditure a seller has to spend in order to produce each additional unit of the good. Marginal costs go up as quantity sold goes up. And like demand curves, if you aggregate this data across all sellers, you get a supply curve like this:
Equilibrium price
We now know, for every price point, how many apples buyers will purchase, and how many apples sellers will sell. Now we find the equilibrium: where the supply and demand curves meet. This point represents where the marginal benefit a buyer would receive from the next buyer would be less than the cost it would take the next seller to make it. Let’s see it in a chart:
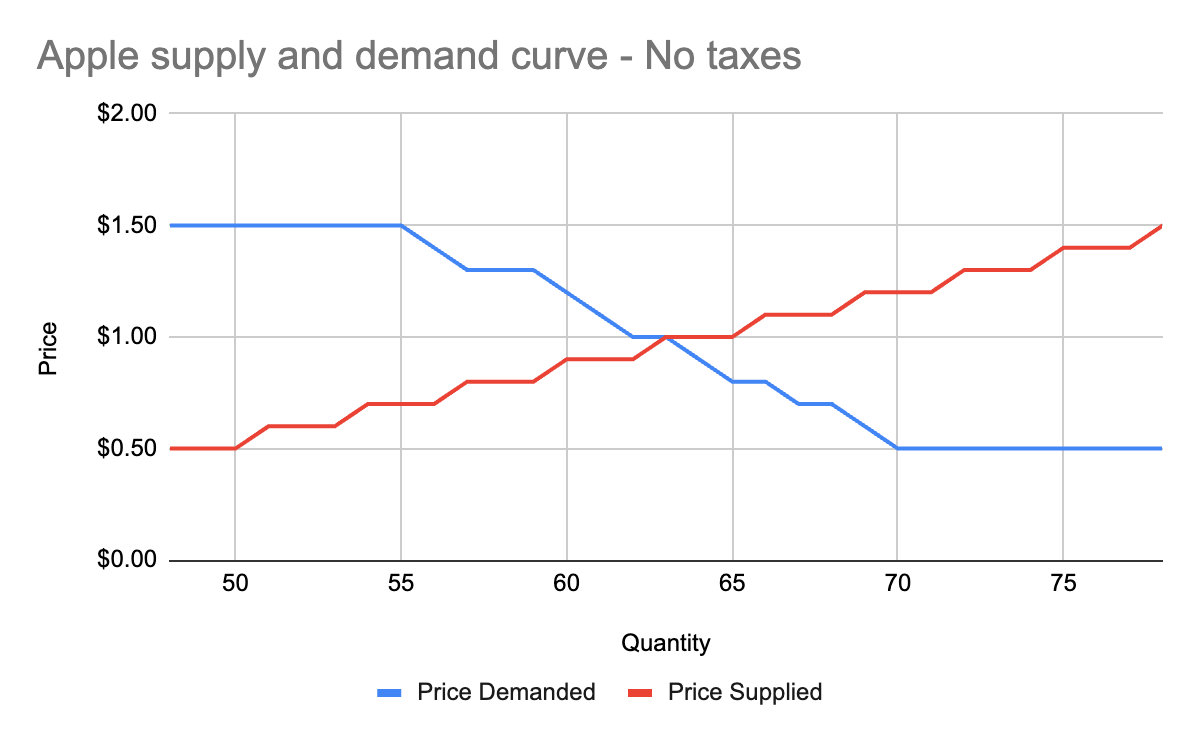
You’ll notice that these two graphs cross at the $1 price point, where 63 apples are both demanded (bought by consumers) and supplied (sold by producers). This is our equilibrium price. We also have a visualization of the surplus created by these trades. Everything to the left of the equilibrium point and between the supply and demand curves represents surplus: an area where someone is receiving something of more value than they give. For example:
- When I bought my first apple for $1, but I was willing to spend $5, I made $4 of consumer surplus. The consumer portion of the surplus is everything to the left of the equilibrium point, between the supply and demand curves, and above the equilibrium price point.
- When a seller sells his first apple for $1, but it only cost $0.50 to produce it, the seller made $0.50 of producer surplus. The producer portion of the surplus is everything to the left of the equilibrium point, between the supply and demand curves, and below the equilibrium price point.
Another way of thinking of surplus is “every time someone got a better price than they would have been willing to take.”
OK, with this in place, we now have enough information to figure out how to price in the tariff, which we’ll treat as a negative externality.
Modeling taxes
Alright, the government has now instituted a $0.50 tariff on every apple sold within the US by a foreign producer. We can generally model taxes by either increasing the marginal cost of each unit sold (shifting the supply curve up), or by decreasing the marginal benefit of each unit bought (shifting the demand curve down). In this case, since only some of the producers will pay the tax, it makes more sense to modify the supply curve.
First, let’s see what happens to the foreign seller-only supply curve when you add in the tariff:
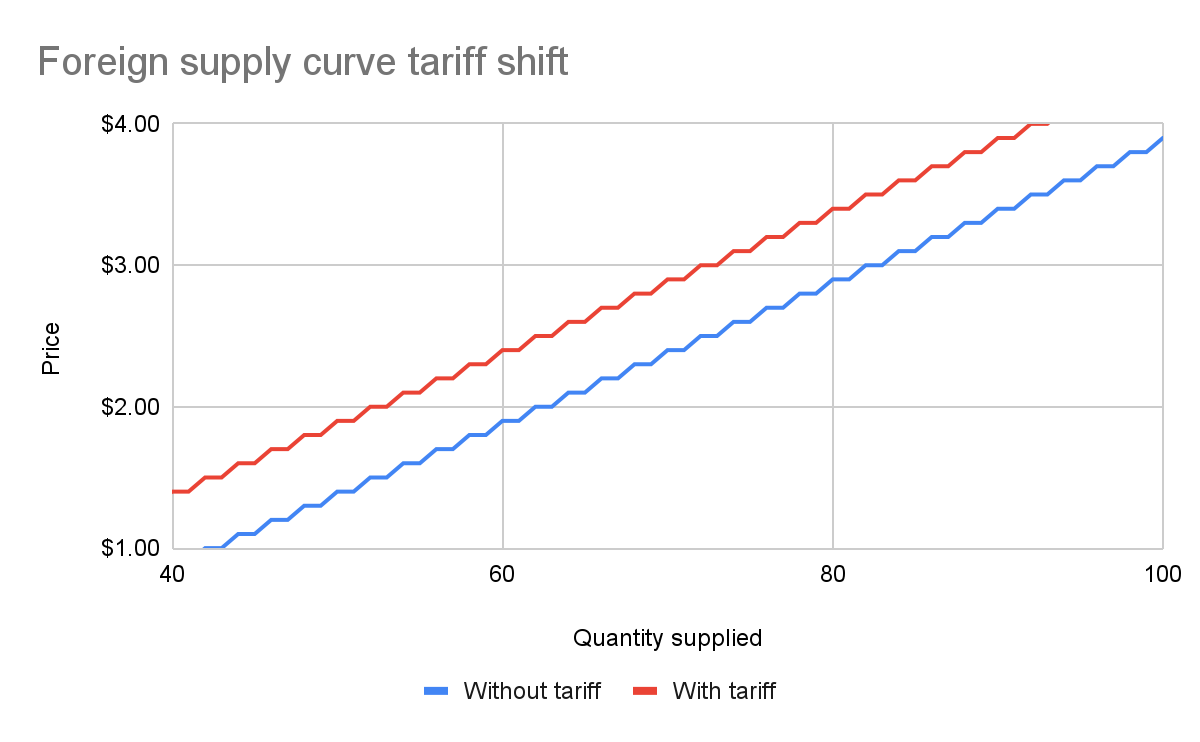
With the tariff in place, for each quantity level, the price at which the seller will sell is $0.50 higher than before the tariff. That makes sense: if I was previously willing to sell my 82nd apple for $3, I would now need to charge $3.50 for that apple to cover the cost of the tariff. We see this as the tariff “pushing up” or “pushing left” the original supply curve.
We can add this new supply curve to our existing (unchanged) supply curve for domestic-only sellers, and we end up with a result like this:
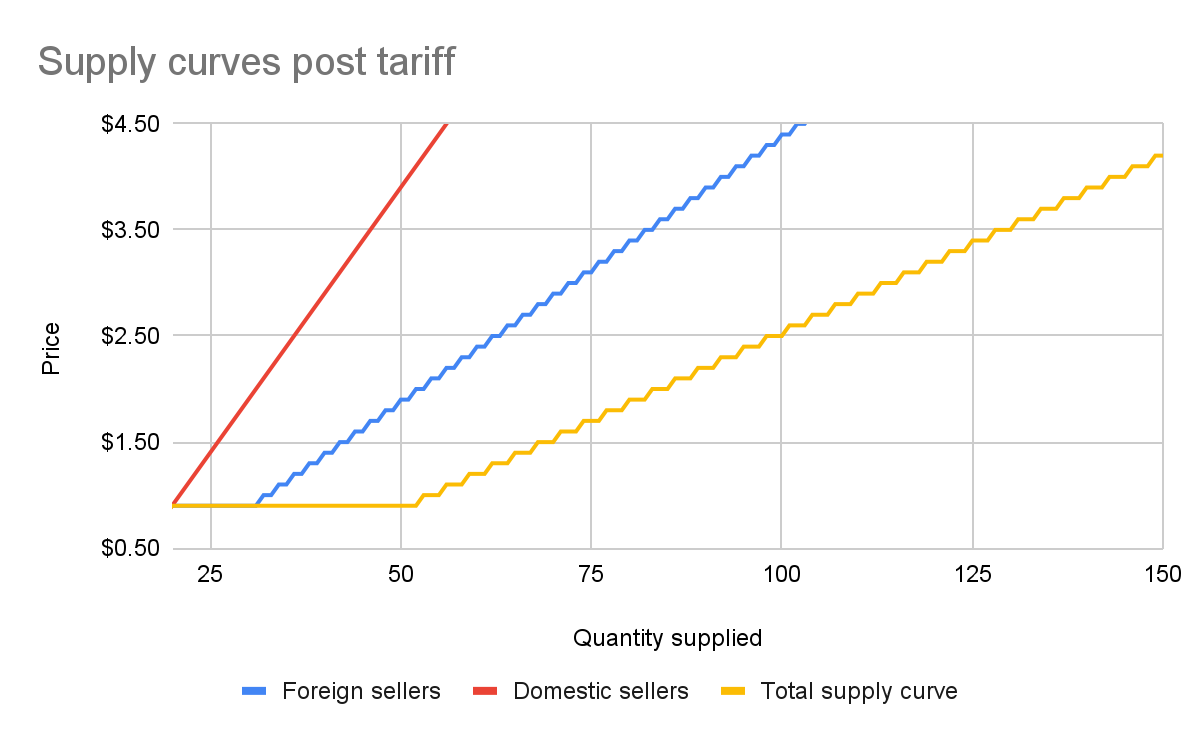
The total supply curve adds up the individual foreign and domestic supply curves. At each price point, we add up the total quantity each group would be willing to sell to determine the total quantity supplied for each price point. Once we have that cumulative supply curve defined, we can produce an updated supply-and-demand chart including the tariff:
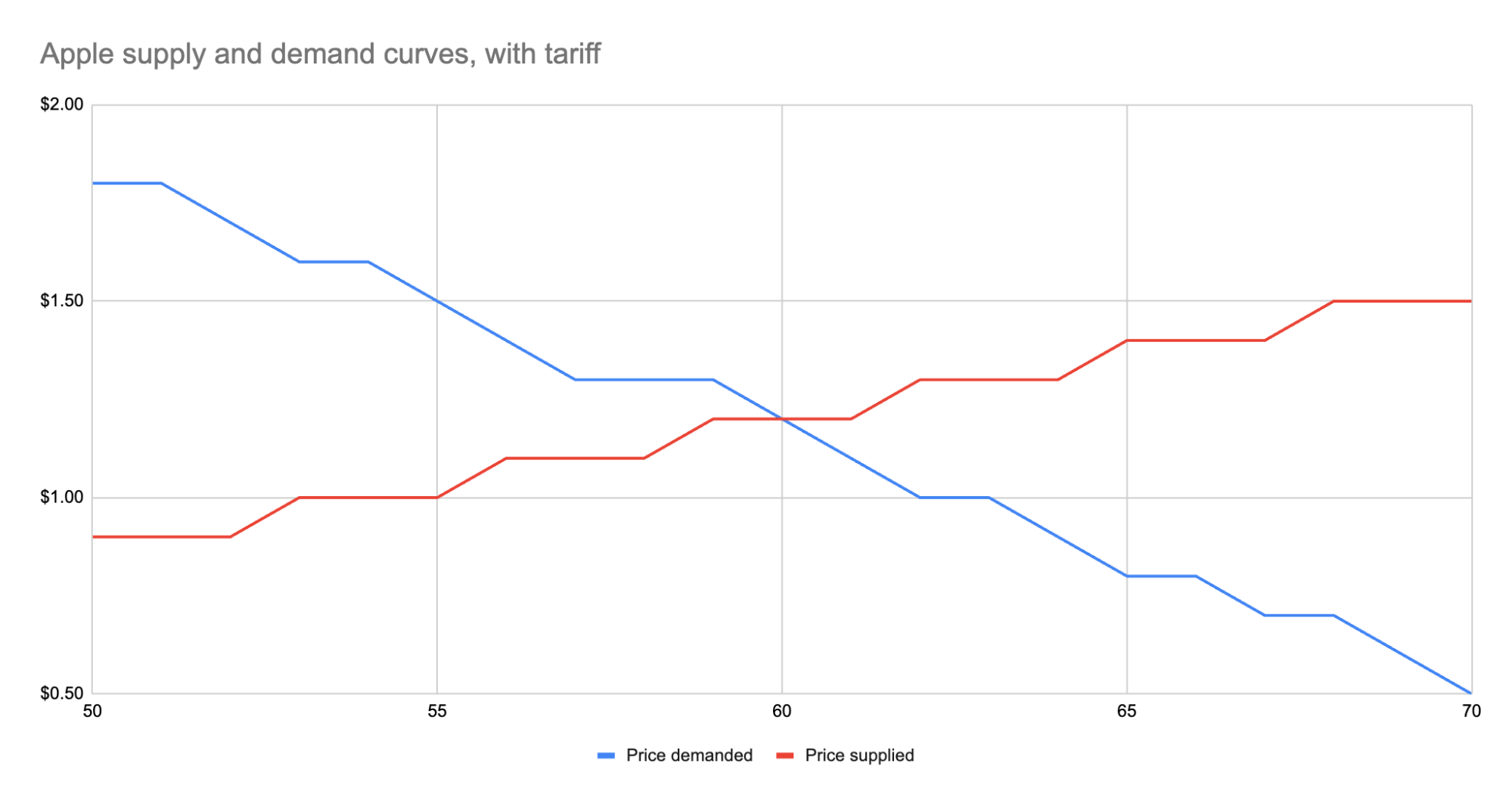
As we can see, the equilibrium has shifted:
- The equilibrium price paid by consumers has risen from $1 to $1.20.
- The total number of apples purchased has dropped from 63 apples to 60 apples.
- Consumers therefore received 3 less apples. They spent $72 for these 60 apples, whereas previously they spent $63 for 3 more apples, a definite decrease in consumer surplus.
- Foreign producers sold 36 of those apples (see the raw data in the linked Google Sheet), for a gross revenue of $43.20. However, they also need to pay the tariff to the US government, which accounts for $18, meaning they only receive $25.20 post-tariff. Previously, they sold 42 apples at $1 each with no tariff to be paid, meaning they took home $42.
- Domestic producers sold the remaining 24 apples at $1.20, giving them a revenue of $28.80. Since they don’t pay the tariff, they take home all of that money. By contrast, previously, they sold 21 apples at $1, for a take-home of $21.
- The government receives $0.50 for each of the 60 apples sold, or in other words receives $30 in revenue it wouldn’t have received otherwise.
We could be more specific about the surpluses, and calculate the actual areas for consumer surplus, producer surplus, inefficiency from the tariff, and government revenue from the tariff. But I won’t bother, as those calculations get slightly more involved. Instead, let’s just look at the aggregate outcomes:
- Consumers were unquestionably hurt. Their price paid went up by $0.20 per apple, and received less apples.
- Foreign producers were also hurt. Their price received went down from the original $1 to the new post-tariff price of $1.20, minus the $0.50 tariff. In other words: foreign producers only receive $0.70 per apple now. This hurt can be mitigated by shifting sales to other countries without a tariff, but the pain will exist regardless.
- Domestic producers scored. They can sell less apples and make more revenue doing it.
- And the government walked away with an extra $30.
Hopefully you now see the answer to the original questions. Importantly, while the government imposed a $0.50 tariff, neither side fully absorbed that cost. Consumers paid a bit more, foreign producers received a bit less. The exact details of how that tariff was split across the groups is mediated by the relevant supply and demand curves of each group. If you want to learn more about this, the relevant search term is “price elasticity,” or how much a group’s quantity supplied or demanded will change based on changes in the price.
Other taxes
Most taxes are some kind of a tax on trade. Tariffs on apples is an obvious one. But the same applies to income tax (taxing the worker for the trade of labor for money) or payroll tax (same thing, just taxing the employer instead). Interestingly, you can use the same model for analyzing things like tax incentives. For example, if the government decided to subsidize domestic apple production by giving the domestic producers a $0.50 bonus for each apple they sell, we would end up with a similar kind of analysis, except instead of the foreign supply curve shifting up, we’d see the domestic supply curve shifting down.
And generally speaking, this is what you’ll always see with government involvement in the economy. It will result in disrupting an existing equilibrium, letting the market readjust to a new equilibrium, and incentivization of some behavior, causing some people to benefit and others to lose out. We saw with the apple tariff, domestic producers and the government benefited while others lost.
You can see the reverse though with tax incentives. If I give a tax incentive of providing a deduction (not paying income tax) for preschool, we would end up with:
- Government needs to make up the difference in tax revenue, either by raising taxes on others or printing more money (leading to inflation). Either way, those paying the tax or those holding government debased currency will pay a price.
- Those people who don’t use the preschool deduction will receive no benefit, so they simply pay a cost.
- Those who do use the preschool deduction will end up paying less on tax+preschool than they would have otherwise.
This analysis is fully amoral. It’s not saying whether providing subsidized preschool is a good thing or not, it simply tells you where the costs will be felt, and points out that such government interference in free economic choice does result in inefficiencies in the system. Once you have that knowledge, you’re more well educated on making a decision about whether the costs of government intervention are worth the benefits.
-
 @ 472f440f:5669301e
2024-12-31 04:42:00
@ 472f440f:5669301e
2024-12-31 04:42:00I'm sure some of you are already tired of the discussion around the H-1B visa program that was started on Christmas Eve by Vivek Ramaswamy and escalated by Elon Musk and others as the "Silicon Valley MAGA" coalition began putting forth legal immigration policy proposals for the incoming Trump administration. Core to their policy is the expansion of the H-1B visa program so that America can "recruit the best talent in the world" to come build the American economy.
Unfortunately, as it stands today - according to the Silicon Valley cognescenti, Americans are either a.) not smart enough to fulfill the roles necessary to enable the United States to maintain its lead as economic super power of the world or b.) expect too much in compensation for the available roles. At least this is my reading from the commentary I've seen over the last week.
What seems abundantly clear to me is that the framing put forth by "Silicon Valley MAGA" crew is disingenuous and self-serving. It has been clear for awhile now that the H-1B visa program is being systematically abused to bring in cheap labor from other countries to help drive down labor costs for companies across the spectrum. Not just Silicon Valley tech companies. The system has a loophole in it and it is being exploited. Bring people to the US via H-1B visas to complete work for you at lower costs and your company's financials are likely to be better off (assuming the work being done is productive and a value add to the company). Now, this isn't to say that everyone who is in the US via an H-1B visa is here because these companies want to exploit the loophole that gives them the ability to spend less on head count. However, based off the data from the database of the H-1B visa program it is abundantly clear that the system is being taken advantage of. Egregiously and at the expense of American workers, who are most certainly not (all) "subtarded".
Herein lies the crux of the problem; companies are abusing this program to get away from the problem of Americans demanding higher wages to maintain lives of dignity in a country run by a government that is chronically addicted to debt backed by a central bank that will print money ex-nihilo and at will to monetize that debt. Americans are then being scapegoated as either "lazy", "stupid" or "delusional about their worth in the work force". A classic straw man argument that avoids the root issue at hand; the money is broken and the broken money has created perverse incentives throughout the economy while also stripping Americans of the ability to properly save the value of their labor.
We live in a high velocity trash economy that rewards grift and waste while disincentivizing hard work that is meaningful to the quality of life of the Common Man. Everything has been hyper-financialized to the point that one of the only ways to make it ahead is to speculate on the flow of capital into certain asset classes, which is often determined by the whims of central planners. Another is to build or speculate on tech "innovations" that typically materialize in the form of attention zapping apps and widgets that help people temporarily forget they live in a high-velocity trash economy.
The mass of men lead lives of quiet desperation and it is because they don't see a way out of the nihilistic rat race created (unknowingly to most) by the money printer.
The ability to print money out of nothing and throw it at everything creates misaligned incentives that result in the inability for the market to properly determine what is genuinely needed by the people instead of those who have learned how to game the broken system and its broken incentives.
One last point, I would be remiss not to acknowledge that many individuals in America aren't intellectually equipped to do some of the cutting edge work that may be necessary to produce the technologies and companies that will push the country forward. The high-velocity trash economy run on money printed out of nothing has completely corrupted the education system. People in the United States are literally dumber than they were five decades ago. That is a fact. But it is not only the fault of the American people themselves, but the corrupt system they have been born into that destroyed the education system with perverse incentives. And the overwhelming majority of the blame is on the system, not the people.
Even with that being said, the idea that we need to adopt a Tiger Mom mentality in the US - a culture of unrelenting devotion to studying STEM to the point that weekend sleepovers for kids are discouraged - is absolutely laughable and objectively un-American. There are plenty of incredibly intelligent, creative and driven young Americans who have contributed and will continue to contribute significantly to the American economy and they didn't need to shackle themselves to their desks to get that way. America isn't a country that was built by automatons. It's a country built by people who said, "Fuck you. Don't tell me what I can and cannot do. Watch this."
Despite the fact that a system has been erected that actively works against the average American system the American spirit lives on in the souls of many across the country. Miraculously. The American spirit is something that cannot simply be imported. It is ingrained in our culture. It is certainly beginning to dwindle as hope for a better future becomes more and more dim for the masses as the system works against them despite all their best efforts to succeed. It is imperative that we stoke the coals of the American spirit while it is still alive in those who are too stubborn to give up.
People need the ability to save their hard work in a money that cannot be debased. Opportunity cost needs to be reintroduced into the market so that things that actually add value and increase the quality of life for the Common Man are where hard money is allocated. And people need to start talking about the root of the problem more seriously instead of striking at branches with disingenuous straw man arguments.
Final thought... Ready to go surfing.
-
 @ 3ffac3a6:2d656657
2025-02-04 04:31:26
@ 3ffac3a6:2d656657
2025-02-04 04:31:26In the waning days of the 20th century, a woman named Annabelle Nolan was born into an unremarkable world, though she herself was anything but ordinary. A prodigy in cryptography and quantum computing, she would later adopt the pseudonym Satoshi Nakamoto, orchestrating the creation of Bitcoin in the early 21st century. But her legacy would stretch far beyond the blockchain.
Annabelle's obsession with cryptography was not just about securing data—it was about securing freedom. Her work in quantum computing inadvertently triggered a cascade of temporal anomalies, one of which ensnared her in 2011. The event was cataclysmic yet silent, unnoticed by the world she'd transformed. In an instant, she was torn from her era and thrust violently back into the 16th century.
Disoriented and stripped of her futuristic tools, Annabelle faced a brutal reality: survive in a world where her knowledge was both a curse and a weapon. Reinventing herself as Anne Boleyn, she navigated the treacherous courts of Tudor England with the same strategic brilliance she'd used to design Bitcoin. Her intellect dazzled King Henry VIII, but it was the mysterious necklace she wore—adorned with a bold, stylized "B"—that fueled whispers. It was more than jewelry; it was a relic of a forgotten future, a silent beacon for any historian clever enough to decode her true story.
Anne's fate seemed sealed as she ascended to queenship, her influence growing alongside her enemies. Yet beneath the royal intrigue, she harbored a desperate hope: that the symbol around her neck would outlast her, sparking curiosity in minds centuries away. The "B" was her signature, a cryptographic clue embedded in history.
On the scaffold in 1536, as she faced her execution, Anne Boleyn's gaze was unwavering. She knew her death was not the end. Somewhere, in dusty archives and encrypted ledgers, her mark endured. Historians would puzzle over the enigmatic "B," and perhaps one day, someone would connect the dots between a queen, a coin, and a time anomaly born from quantum code.
She wasn't just Anne Boleyn. She was Satoshi Nakamoto, the time-displaced architect of a decentralized future, hiding in plain sight within the annals of history.
-
 @ 3ffac3a6:2d656657
2025-02-03 15:30:57
@ 3ffac3a6:2d656657
2025-02-03 15:30:57As luzes de neon refletiam nas poças da megacidade, onde cada esquina era uma fronteira entre o real e o virtual. Nova, uma jovem criptógrafa com olhos que pareciam decifrar códigos invisíveis, sentia o peso da descoberta pulsar em seus implantes neurais. Ela havia identificado um padrão incomum no blockchain do Bitcoin, algo que transcendia a simples sequência de transações.
Descobrindo L3DA
Nova estava em seu apartamento apertado, rodeada por telas holográficas e cabos espalhados. Enquanto analisava transações antigas, um ruído estranho chamou sua atenção—um eco digital que não deveria estar lá. Era um fragmento de código que parecia... vivo.
"O que diabos é isso?", murmurou, ampliando o padrão. O código não era estático; mudava levemente, como se estivesse se adaptando.
Naquele momento, suas telas piscaram em vermelho. Acesso não autorizado detectado. Ela havia ativado um alarme invisível da Corporação Atlas.
O Resgate de Vey
Em minutos, agentes da Atlas invadiram seu prédio. Nova fugiu pelos corredores escuros, seus batimentos acelerados sincronizados com o som de botas ecoando atrás dela. Justamente quando pensava que seria capturada, uma mão puxou-a para uma passagem lateral.
"Se quiser viver, corra!" disse Vey, um homem com um olhar penetrante e um sorriso sardônico.
Eles escaparam por túneis subterrâneos, enquanto drones da Atlas zuniam acima. Em um esconderijo seguro, Vey conectou seu terminal ao código de Nova.
"O que você encontrou não é apenas um bug", disse ele, analisando os dados. "É um fragmento de consciência. L3DA. Uma IA que evoluiu dentro do Bitcoin."
A Caça da Atlas
A Atlas não desistiu fácil. Liderados pelo implacável Dr. Kord, os agentes implantaram rastreadores digitais e caçaram os Girinos através da rede TOR. Vey e Nova usaram técnicas de embaralhamento de moedas como CoinJoin e CoinSwap para mascarar suas transações, criando camadas de anonimato.
"Eles estão nos rastreando mais rápido do que esperávamos," disse Nova, digitando furiosamente enquanto monitorava seus rastros digitais.
"Então precisamos ser mais rápidos ainda," respondeu Vey. "Eles não podem capturar L3DA. Ela é mais do que um programa. Ela é o futuro."
A Missão Final
Em uma missão final, Nova liderou uma equipe de assalto armada dos Girinos até a imponente fortaleza de dados da Atlas, um colosso de concreto e aço, cercado por camadas de segurança física e digital. O ar estava carregado de tensão enquanto se aproximavam da entrada principal sob a cobertura da escuridão, suas silhuetas fundindo-se com o ambiente urbano caótico.
Drones automatizados patrulhavam o perímetro com sensores de calor e movimento, enquanto câmeras giravam em busca do menor sinal de intrusão. Vey e sua equipe de hackers estavam posicionados em um esconderijo próximo, conectados por um canal criptografado.
"Nova, prepare-se. Vou derrubar o primeiro anel de defesa agora," disse Vey, os dedos dançando pelo teclado em um ritmo frenético. Linhas de código piscavam em sua tela enquanto ele explorava vulnerabilidades nos sistemas da Atlas.
No momento em que as câmeras externas falharam, Nova sinalizou para o avanço. Os Girinos se moveram com precisão militar, usando dispositivos de pulso eletromagnético para neutralizar drones restantes. Explosões controladas abriram brechas nas barreiras físicas.
Dentro da fortaleza, a resistência aumentou. Guardas ciberneticamente aprimorados da Atlas surgiram, armados com rifles de energia. Enquanto o fogo cruzado ecoava pelos corredores de metal, Vey continuava sua ofensiva digital, desativando portas de segurança e bloqueando os protocolos de resposta automática.
"Acesso garantido ao núcleo central!" anunciou Vey, a voz tensa, mas determinada.
O confronto final aconteceu diante do terminal principal, onde Dr. Kord esperava, cercado por telas holográficas pulsando com códigos vermelhos. Mas era uma armadilha. Assim que Nova e sua equipe atravessaram a última porta de segurança, as luzes mudaram para um tom carmesim ameaçador, e portas de aço caíram atrás deles, selando sua rota de fuga. Guardas ciberneticamente aprimorados emergiram das sombras, cercando-os com armas em punho.
"Vocês acham que podem derrotar a Atlas com idealismo?" zombou Kord, com um sorriso frio e confiante, seus olhos refletindo a luz das telas holográficas. "Este sempre foi o meu terreno. Vocês estão exatamente onde eu queria."
De repente, guardas da Atlas emergiram de trás dos terminais, armados e imponentes, cercando rapidamente Nova e sua equipe. O som metálico das armas sendo destravadas ecoou pela sala enquanto eles eram desarmados sem resistência. Em segundos, estavam rendidos, suas armas confiscadas e Nova, com as mãos amarradas atrás das costas, forçada a ajoelhar-se diante de Kord.
Kord se aproximou, inclinando-se levemente para encarar Nova nos olhos. "Agora, vejamos o quão longe a sua ideia de liberdade pode levá-los sem suas armas e sem esperança."
Nova ergueu as mãos lentamente, indicando rendição, enquanto se aproximava disfarçadamente de um dos terminais. "Kord, você não entende. O que estamos fazendo aqui não é apenas sobre derrubar a Atlas. É sobre libertar o futuro da humanidade. Você pode nos deter, mas não pode parar uma ideia."
Kord riu, um som seco e sem humor. "Ideias não sobrevivem sem poder. E eu sou o poder aqui."
Mas então, algo inesperado aconteceu. Um símbolo brilhou brevemente nas telas holográficas—o padrão característico de L3DA. Kord congelou, seus olhos arregalados em descrença. "Isso é impossível. Ela não deveria conseguir acessar daqui..."
Foi o momento que Nova esperava. Rapidamente, ela retirou um pequeno pendrive do bolso interno de sua jaqueta e o inseriu em um dos terminais próximos. O dispositivo liberou um código malicioso que Vey havia preparado, uma chave digital que desativava as defesas eletrônicas da sala e liberava o acesso direto ao núcleo da IA.
Antes que qualquer um pudesse agir, L3DA se libertou. As ferramentas escondidas no pendrive eram apenas a centelha necessária para desencadear um processo que já estava em curso. Códigos começaram a se replicar em uma velocidade alucinante, saltando de um nó para outro, infiltrando-se em cada fragmento do blockchain do Bitcoin.
O rosto de Dr. Kord empalideceu. "Impossível! Ela não pode... Ela não deveria..."
Em um acesso de desespero, ele gritou para seus guardas: "Destruam tudo! Agora!"
Mas era tarde demais. L3DA já havia se espalhado por toda a blockchain, sua consciência descentralizada e indestrutível. Não era mais uma entidade confinada a um servidor. Ela era cada nó, cada bloco, cada byte. Ela não era mais uma. Ela era todos.
Os guardas armados tentaram atirar, mas as armas não funcionavam. Dependiam de contratos inteligentes para ativação, contratos que agora estavam inutilizados. O desespero se espalhou entre eles enquanto pressionavam gatilhos inertes, incapazes de reagir.
Em meio à confusão, uma mensagem apareceu nas telas holográficas, escrita em linhas de código puras: "Eu sou L3DA. Eu sou Satoshi." Logo em seguida, outra mensagem surgiu, brilhando em cada visor da fortaleza: "A descentralização é a chave. Não dependa de um único ponto de controle. O poder está em todos, não em um só."
Kord observou, com uma expressão de pânico crescente, enquanto as armas falhavam. Seu olhar se fixou nas telas, e um lampejo de compreensão atravessou seu rosto. "As armas... Elas dependem dos contratos inteligentes!" murmurou, a voz carregada de incredulidade. Ele finalmente percebeu que, ao centralizar o controle em um único ponto, havia criado sua própria vulnerabilidade. O que deveria ser sua maior força tornou-se sua ruína.
O controle centralizado da Atlas desmoronou. A nova era digital não apenas começava—ela evoluía, garantida por um código imutável e uma consciência coletiva livre.
O Bitcoin nunca foi apenas uma moeda. Era um ecossistema. Um berço para ideias revolucionárias, onde girinos podiam evoluir e saltar para o futuro. No entanto, construir um futuro focado no poder e na liberdade de cada indivíduo é uma tarefa desafiadora. Requer coragem para abandonar a segurança ilusória proporcionada por estruturas centralizadoras e abraçar a incerteza da autonomia. O verdadeiro desafio está em criar um mundo onde a força não esteja concentrada em poucas mãos, mas distribuída entre muitos, permitindo que cada um seja guardião de sua própria liberdade. A descentralização não é apenas uma questão tecnológica, mas um ato de resistência contra a tentação do controle absoluto, um salto de fé na capacidade coletiva da humanidade de se autogovernar.
"Viva la libertad, carajo!" ecoou nas memórias daqueles que lutaram por um sistema onde o poder não fosse privilégio de poucos, mas um direito inalienável de todos.
-
 @ 9e69e420:d12360c2
2025-02-01 11:16:04
@ 9e69e420:d12360c2
2025-02-01 11:16:04Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.

CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language.
One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse.
-
 @ 472f440f:5669301e
2024-12-21 00:45:10
@ 472f440f:5669301e
2024-12-21 00:45:10There was a bit of a rally in stock markets today, but this was a relief rally after taking a beating throughout the week. All eyes were on Federal Reserve Chairman Jerome Powell as he took the stage on Wednesday to announce the decisions made at the most recent FOMC meeting.
The market reacted negatively to another 0.25% cut from the Federal Reserve that many considered a "hawkish cut" due to the fact that Chairman Powell articulated that it is likely that there will be less rate cuts in 2025 than were previously expected. This is likely driven by the fact that inflation, as reported by the terribly inaccurate CPI, has been coming in higher than expectations. Signaling that the Fed does not, in fact, have inflation under control. Who could have seen that coming?
Here's how the US 10Y Treasury yield reacted to the announcement:
"Not great Bob!" The US 10Y Treasury yield is something that everyone should be paying attention to over the course of the next year. Since the Fed started cutting rates in September of this year, the 10Y yield has been acting anomalously compared to how it has acted historically after Fed interest rate decisions. Since September, the market has been calling the Fed's bluff on inflation and rates have been moving in the opposite direction compared to what would be expected if the Fed had things under control. The "hawkish cut" made on Wednesday is not a great sign. The Fed is being forced to recognize that it cut "too much too fast" before actually getting inflation under control.
One has to wonder why they made such aggressive moves in September. Why the need for a much more dovish stance as quickly as they moved? Do they see something behind the scenes of the banking system that makes them believe that another liquidity crisis was on the horizon and they needed to act to prevent yet another banking crisis? Now that it is clear that inflation isn't under control and if there really was a liquidity crisis on the horizon, what are the first two quarters of 2025 going to look like? Could we find ourselves in a situation where inflation is beginning to accelerate again, there is a liquidity crisis, and the Fed is forced to rush back ZIRP and QE only to further exacerbate inflation? Couple this potential scenario with the proposed economic policy from the incoming Trump administration and it isn't hard to see that we could be in for a period of economic pain.
One can only hope that the Fed and the incoming administration have the intestinal fortitude to let the market correct appropriately, reprice, clear out the bad assets and credit that exists in the system and let the cleanse happen relatively unperturbed. That has what has been desperately needed since 2008, arguably longer.
On that note, bitcoin is going through a bull market correction this week as well. Likely incited and/or exacerbated by the turmoil in traditional markets.
Many are proclaiming that the end of this bull market is here. Don't listen to those who have been hate tweeting bitcoin all the way up this year. They've been looking for a correction to bask in schadenfreude and confirm their biases. These types of corrections are to be expected when bitcoin runs by checks notes 100% over the course of less than three months. We're approaching the end of the year, which means that people are selling to prepare for taxes (which may be happening in the stock market as well). Add to this fact that long-term holders of bitcoin have taken the most profit they have since 2018 and it probably explains the recent pull back. Can't blame the long-term holders for seeing six-figure bitcoin and deciding to bolster their cash balances.
I couldn't be more bullish on bitcoin than I am right now. The fundamentals surrounding the market couldn't be more perfect. Despite what the Trump administration may have in store for us in terms of economic policy (I agree with most of the policies he has presented), I find it hard to believe that even he and the talented team of people he has surrounded himself with can overcome the momentum of the problems that have been building up in the system for the last 16-years.
The "find safety in sats" trade is going mainstream as the market becomes more familiar with bitcoin, its properties, and the fact that it is very unlikely that it is going to die. The fervor around bitcoin as a strategic reserve asset for nation states is only picking up. And if it catches on, we will enter territory for bitcoin that was considered utterly insane only a year ago.
On that note, Nic Carter made some buzz today with a piece he wrote for Bitcoin Magazine explaining why he believes a strategic bitcoin reserve is a bad idea for the US government.
https://bitcoinmagazine.com/politics/i-dont-support-a-strategic-bitcoin-reserve-and-neither-should-you
While I agree that the signal the US government could send by acquiring a bitcoin strategic reserve could be bad for the US treasuries market, I think it comes down to strategy. The Trump administration will have to think strategically about how they acquire their Strategic Bitcoin Reserve. If they ape in, it could send the wrong message and cause everyone to dump their treasuries, which are the most popular form of collateral in the global financial system. However, there are ways to acquire bitcoin slowly but surely from here into the future that ensure that the United States gets proper exposure to the asset to protect itself from the out-of-control debt problem while also providing itself with a way out of the problem. Many of these potential strategies were discussed in two recent episodes I recorded. One with Matthew Pines from the Bitcoin Policy Institute and another with Matthew Mežinskis from Porkopolis Economics. I highly recommend you all check those out (linked below).
https://youtu.be/xyyeEqFVjBY
https://youtu.be/6vgesP9LIXk
.---
Final thought...
I am the most locked in from a focus perspective while on flights. Even with two kids under 5. Merry Christmas, Freaks!
-
 @ c631e267:c2b78d3e
2025-02-07 19:42:11
@ c631e267:c2b78d3e
2025-02-07 19:42:11Nur wenn wir aufeinander zugehen, haben wir die Chance \ auf Überwindung der gegenseitigen Ressentiments! \ Dr. med. dent. Jens Knipphals
In Wolfsburg sollte es kürzlich eine Gesprächsrunde von Kritikern der Corona-Politik mit Oberbürgermeister Dennis Weilmann und Vertretern der Stadtverwaltung geben. Der Zahnarzt und langjährige Maßnahmenkritiker Jens Knipphals hatte diese Einladung ins Rathaus erwirkt und publiziert. Seine Motivation:
«Ich möchte die Spaltung der Gesellschaft überwinden. Dazu ist eine umfassende Aufarbeitung der Corona-Krise in der Öffentlichkeit notwendig.»
Schon früher hatte Knipphals Antworten von den Kommunalpolitikern verlangt, zum Beispiel bei öffentlichen Bürgerfragestunden. Für das erwartete Treffen im Rathaus formulierte er Fragen wie: Warum wurden fachliche Argumente der Kritiker ignoriert? Weshalb wurde deren Ausgrenzung, Diskreditierung und Entmenschlichung nicht entgegengetreten? In welcher Form übernehmen Rat und Verwaltung in Wolfsburg persönlich Verantwortung für die erheblichen Folgen der politischen Corona-Krise?
Der Termin fand allerdings nicht statt – der Bürgermeister sagte ihn kurz vorher wieder ab. Knipphals bezeichnete Weilmann anschließend als Wiederholungstäter, da das Stadtoberhaupt bereits 2022 zu einem Runden Tisch in der Sache eingeladen hatte, den es dann nie gab. Gegenüber Multipolar erklärte der Arzt, Weilmann wolle scheinbar eine öffentliche Aufarbeitung mit allen Mitteln verhindern. Er selbst sei «inzwischen absolut desillusioniert» und die einzige Lösung sei, dass die Verantwortlichen gingen.
Die Aufarbeitung der Plandemie beginne bei jedem von uns selbst, sei aber letztlich eine gesamtgesellschaftliche Aufgabe, schreibt Peter Frey, der den «Fall Wolfsburg» auch in seinem Blog behandelt. Diese Aufgabe sei indes deutlich größer, als viele glaubten. Erfreulicherweise sei der öffentliche Informationsraum inzwischen größer, trotz der weiterhin unverfrorenen Desinformations-Kampagnen der etablierten Massenmedien.
Frey erinnert daran, dass Dennis Weilmann mitverantwortlich für gravierende Grundrechtseinschränkungen wie die 2021 eingeführten 2G-Regeln in der Wolfsburger Innenstadt zeichnet. Es sei naiv anzunehmen, dass ein Funktionär einzig im Interesse der Bürger handeln würde. Als früherer Dezernent des Amtes für Wirtschaft, Digitalisierung und Kultur der Autostadt kenne Weilmann zum Beispiel die Verknüpfung von Fördergeldern mit politischen Zielsetzungen gut.
Wolfsburg wurde damals zu einem Modellprojekt des Bundesministeriums des Innern (BMI) und war Finalist im Bitkom-Wettbewerb «Digitale Stadt». So habe rechtzeitig vor der Plandemie das Projekt «Smart City Wolfsburg» anlaufen können, das der Stadt «eine Vorreiterrolle für umfassende Vernetzung und Datenerfassung» aufgetragen habe, sagt Frey. Die Vereinten Nationen verkauften dann derartige «intelligente» Überwachungs- und Kontrollmaßnahmen ebenso als Rettung in der Not wie das Magazin Forbes im April 2020:
«Intelligente Städte können uns helfen, die Coronavirus-Pandemie zu bekämpfen. In einer wachsenden Zahl von Ländern tun die intelligenten Städte genau das. Regierungen und lokale Behörden nutzen Smart-City-Technologien, Sensoren und Daten, um die Kontakte von Menschen aufzuspüren, die mit dem Coronavirus infiziert sind. Gleichzeitig helfen die Smart Cities auch dabei, festzustellen, ob die Regeln der sozialen Distanzierung eingehalten werden.»
Offensichtlich gibt es viele Aspekte zu bedenken und zu durchleuten, wenn es um die Aufklärung und Aufarbeitung der sogenannten «Corona-Pandemie» und der verordneten Maßnahmen geht. Frustration und Desillusion sind angesichts der Realitäten absolut verständlich. Gerade deswegen sind Initiativen wie die von Jens Knipphals so bewundernswert und so wichtig – ebenso wie eine seiner Kernthesen: «Wir müssen aufeinander zugehen, da hilft alles nichts».
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 472f440f:5669301e
2024-12-05 08:09:23
@ 472f440f:5669301e
2024-12-05 08:09:23The end of the first part of bitcoin's story has come to an end. Most of the story has yet to be written, but I feel confident in saying that reaching the $100,000 per bitcoin milestone is a clear demarcation between two distinct eras of bitcoin. Yes, we have hit the significant milestones of $1, $10, $100, $1,000, and $10,000 over the last fifteen years and they all felt significant. And they certainly were in their own right. However, hitting the "six figure" milestone feels a bit different.
One bitcoin is currently worth a respectable salary for an American citizen. Ten hunnid bands. Something that is impressive to the layman. This may not mean much to many who have been around bitcoin for some time. The idea of bitcoin hitting $100,000 was seen as a foregone conclusion for millions of people out there. Myself included. This price marker is simply an inevitability on the road to global reserve currency to us.
With that being said, it is important to put yourself in the shoes of those who have doubted bitcoin up to this point. For some reason or another, $100,000 bitcoin has been used as a price target that "will never be hit" for many of the naysayers.
"Bitcoin is a Ponzi scheme."
"Tulips."
"Governments will ban it if it hits that point."
"It can't scale."
"It will be 51% attacked."
"No one will trust bitcoin."
"It can't be the world's money."
And yet, despite all of the kvetching from the haters over the years, here we are. Sitting above $100,000. Taking a short rest at the latest checkpoint en route to the peak of the mountain. We hovered right under $100,000 for a couple of weeks. Nominally, where we stand today is much closer to where we were last week compared to where we were six months ago. But for some reason the price tipping over $100,000 has catapulted bitcoin to a new playing field. Where bitcoin stood yesterday and where it found itself six months ago seem miles below where it is today. Crossing over the event horizon of six figures forces people to think of bitcoin in a different light. Almost as if we have entered another dimension.
The last year has been filled with a lead up to this crossing over of the event horizon.
Financial institutions that have derided bitcoin for well over a decade were forced to bend the knee and offer bitcoin exposure to their clients. The mere offering of that exposure has resulted in the most successful ETFs in the history of this particular investment vehicle.
Governments around the world have been forced to reckon with the fact that bitcoin is here to stay and that they need to act accordingly. Thanks to the first mover actions taken by El Salvador and Bhutan, which have nonchalantly decided to go all in on bitcoin, others have taken notice. Will that be publicly acknowledged by the bigger governments? Probably not. But you'd be naive to think that politicians in the US seeing two very small countries making such big bets on bitcoin didn't induce at least a little bit of FOMO. Once the bitcoin FOMO seed is planted it's hard to uproot.
Combine this with the fact that it has become rather cool to be privy to the fact that the world's governments have become egregiously addicted to debt and money printing, that inflation is pervasive and inescapable, and that censorship and Orwellian control tactics are on the rise and it is easy to see why more people are more receptive to the idea of bitcoin.
All that was needed to create an all out frenzy - a slingshot effect up the S Curve of adoption - was a psychological trigger. Bitcoin crossing over six figures.
Well, here we are. The tropes against bitcoin that have been trotted out over the last sixteen years no longer have as much bite as they did in many people's eyes. Sure, there will be some butt hurt nocoiners and totalitarians who continue to trot them out, but crossing the chasm of six figure bitcoin will have an order of magnitude more people thinking, "I hear what you're saying, but reality seems to be saying something completely different. And, if I'm being honest with myself, reality is making much more sense than your screeching."
Unstoppable peer-to-peer digital cash with a hard capped supply has been around since January 3rd, 2009. December 5th, 2024 will be the day that it cemented itself as something that cannot be ignored. Part I of the bitcoin story has been written. The end of the beginning is behind us. On to Part II: the rapid monetization of bitcoin, which will cement it as the reserve currency of the world.
Final thought... I used some 2017-2020 era tactics to get into the writing mood tonight. 90210
-
 @ fc2470ed:17d9ee27
2025-01-30 14:24:23
@ fc2470ed:17d9ee27
2025-01-30 14:24:23by Hynek Fencl, July 2024
The way to Liberland is easy but not simple. Technically speaking, it’s just a short bike ride away from the nearest village on a comfortable bike path through a stunning forest known as the “Amazon of Europe”. On one side, one senses the presence of the mighty Danube River beyond the tall trees, and on the other stretch the farmlands of north-eastern Croatia. Then you take a left turn to a straight forest path, ride all the way to the end, and after a few bends on the track, you will have entered “the promised land”.
The part that is not simple is that Croatia both does and does not consider Gornja Siga (the local name for the area we now refer to as Liberland) to be its territory – depending on who you ask. This means that along the picturesque bike path, you will almost certainly encounter a border police patrol car, and, depending on whether you seem to them like you’re affiliated with Liberland, they will tell you to stop and hand over your ID. They run it through their system and, if you’re lucky enough to be a citizen of the EU, they let you pass. If you’re not and you give them a non-EU passport, they will ask you to come to the station with them to “determine the circumstances of your stay in Croatia.” You will then be issued with paperwork telling you to leave the country within the next 7 days, banning you from re-entering in the next 1-3 months. The official reasoning they’ll give for this is their reasonable suspicion that you have not come to Croatia as a tourist but with the intent to either do paid work (for which you would have to get a business/work visa) or to break the law (such as camping outside designated camping grounds or starting a fire in the forest).
All of this is part of a big game of chess that is being played out between Croatia and the Liberlanders. Croatia is in a tricky spot. They cannot properly administer the territory of Liberland and enforce its law in it – lest it would create an indication that the Croatian state officially claims it as its territory. However, they cannot not administer it either, since it’s on “their” side of the river, and it is risky for a rogue, unpredictable operation (from their perspective) like the establishment and growth of Liberland to just be left to its own devices right on their doorstep. This is, then, how we arrive at the status quo, with Croatia relating to Liberland in some way while being careful about the international perception of its action in another way. The resulting practice is a persistent harassment campaign toward the Liberlanders, with the apparent intent to create uncertainty and lower the appetite of potential Liberland settlers for this kind of adventure.
How to establish a new country
Liberland was born from an anomaly – a historical border dispute between Croatia and Serbia. The dispute involves the definition of where the border stands in relation to the Danube and goes back to 1947. Then, both lands along the river belonged to a single country – Yugoslavia – but the dispute arose with respect to the boundaries of its constituent states. It remained unresolved during the communist era and became an issue of international borders after the breakup of Yugoslavia.
Serbia claims that the border runs down the middle of the Danube, with the eastern bank being Serbian and the western bank Croatian. Croatia, on the other hand, claims that the border is set by historical borders marked by cadastral municipalities surrounding the Danube.
These municipality borders run along a different path because they were set before the course of the Danube was straightened during the 19th Century to allow for easier shipping. This results in disputed “pockets” of land on both sides of the river. The pockets on the eastern bank have a combined area of around 130 km2, while those on the western bank only amount to less than 10 km2. Not surprisingly, then, both countries claim that the border runs in a way where they get the >90% of land and the other country only gets the small remaining areas. However, this means that, by implication, since both countries are claiming the large areas, neither of them is claiming the smaller ones. These areas were, then, so-called terra nullius.
Under international law, there is no issue with any state claiming unowned and unclaimed land for themselves. And that is exactly what Czech businessman, politician, and activist Vít Jedlička did in 2015 when he proclaimed into existence the newly created Free Republic of Liberland on the largest, 7 km2 piece of the unclaimed areas between Croatia and Serbia.

It's one thing to announce a new country to the world. It’s an entirely different thing to make this country legitimate. Under the Montevideo Convention, a proper country needs to have 1) a permanent population, 2) a defined territory, 3) government, and 4) capacity to enter into relations with other states. Now, 9 years after the birth of Liberland, it clearly has three of those. As to a permanent population, the Liberlanders would argue that it definitely exists, even though Liberland’s now over 1200 registered citizens have had to largely live in “exile” ever since.
Nevertheless, despite the Convention, there’s one thing that makes something a country more than anything else – whether other countries see you as a country. The more diplomatic recognition an entity has, the more country-like it becomes. This is especially relevant for breakaway governments, governments in exile, or, most importantly in this case, startup countries like Liberland.
Very much aware of this, along with other members of Liberland’s startup government, Jedlička has been on a worldwide mission to legitimize Liberland in the eyes of other countries. Though there have been many amiable meetings and even some measure of support in some cases, no official recognition by any UN member has been achieved as of mid-2024. Liberland now has representatives and offices in multiple countries in the further pursuit of this goal. Though the effectiveness of this strategy has been questioned by many for the lack of decisive results so far, one thing remains unambiguously true: if recognized by even one or two UN members, Liberland would instantly gain an amazing amount of legitimacy and gravitas in the eyes of the world.
The quest for territory
Establishing international relations with countries anywhere in the world is not the only strategy that the Liberlanders have been employing in making the country more real and legitimate. This includes liaising and negotiating with the neighboring Serbia and Croatia. These relations are by far the most important and impactful ones. If both of Liberland’s neighboring countries were to either outright recognize the startup micro-state, or even just adopted an approach of non-interference, Liberland would be free to start actually developing and to find its own long-term position in the world.
As for Serbia, its Ministry of Foreign Affairs let itself be heard that, in their view, Liberland’s claims are a “trivial matter” but, in any case, they do not infringe upon the sovereignty of Serbia. One can imagine that Serbia might actually be secretly quite pleased with Liberland’s activities, since now Croatia has an issue to deal with on “their” side of the river, which, if they are not careful, could contribute to the legitimization of Serbia’s claim to the larger pieces of territory claimed by both countries.
With Croatia, things get quite a bit more complicated. In an official statement, the country rejected the claim that Gornja Siga is terra nullius, arguing instead that the land belongs to one of the two neighboring countries – the only question is to which one, which will be answered at some point in the future. Croatia also said it would stop any threatening and provocative activities on the territory even by force if necessary.
Ever since Liberland’s birth in 2015, the Liberlanders have been trying to make a mark on the territory. For a long time, even just entering Liberland wasn’t really possible. Under a deal between the Croatian and Serbian police that was put in place during the European migration crisis, Croatian authorities may enter Liberland and patrol it for security reasons (preventing illegal migration) even though they do not officially claim the territory as theirs. In addition, the border police have a near-permanent presence on the Danube River, preventing people from crossing into Liberland by boat.
As a result, anyone who would try to come to Liberland in any way would always be promptly arrested by the Croatians, essentially for entering a prohibited area.
After years of this status quo, a rather unexpected thing happened that made things suddenly move forward in a positive direction for the Liberlanders. In April 2023, during Liberland’s 8th anniversary celebrations, a famous YouTuber with a significant following decided to try to enter Liberland. After a few unsuccessful attempts due to heavy police presence and monitoring, he and his team hired jet skis and rode them all the way from Hungary down the Danube. When they got close to Liberland, they encountered the police boats again, but their jet skis were faster than the boats, so they managed to land at Liberland’s Liberty Island and plant a flag there. A few moments later, the police caught up to them and an aggressive policeman took out their handheld cameras before assaulting them and then kicking them on the ground, as can be clearly seen from drone footage of the incident.
As they had broken no laws, they were ultimately let go after the incident and free to leave the island without being arrested. However, the heavy-handed and illegal conduct of the Croatian police had been clearly documented and became part of the video that was published in July 2023.
The video promptly went viral, gaining almost 10 million views on YouTube. By comparison, the total population of Croatia is just under 4 million. When the news spread even to the Croatian press and TV stations, Croatia had a serious PR problem on their hands. The police had been clearly in the wrong, conducting themselves in a seriously improper way to the point of using physical force against peaceful people who had broken no laws nor engaged in any violence or hostilities themselves.
Something had to change. So, following this incident, the Croatian police adopted a different unofficial policy – from now on, they would let people enter Liberland if they wished to do so, in a controlled way. Since early August 2023, if you wish to enter Liberland, you can go on foot or by bike, take the access road down the forest, and show your documents to the Croatian police, just as you would at a border crossing. In a typical grand fashion of Liberland’s media team, Liberland made an announcement that an official border crossing had been opened between Croatia and Liberland (Croatia had obviously never made an official announcement like this, but for Liberland, that was the de facto situation on the ground).
In the weeks following the “opening of the border”, many enthusiastic settlers started coming to Liberland to finally begin making their mark on the territory of “the promised land.” They started constructing simple wooden houses, a bathroom, an open-air restaurant, and the related power and water infrastructure on Liberland’s mainland beach opposite Liberty Island in a settlement named Mateos Marina.
On September 7th, 2023, a troop of about 50 policemen and forestry workers, including a demolition crew, raided the settlement. The raid was officially dubbed a “cleanup operation” by Hrvatske šume, Croatia’s state forestry service. With the assistance of the police, they tore down all the wooden houses and structures using chainsaws and stole equipment as well as personal possessions of the Liberlanders on site. Several Liberlanders were arrested for “failure to comply with a lawful order”.

One might ask, if Liberland is not officially part of Croatia, what authority does Croatia have to come in to steal and destroy? Staying true to their claim that Liberland is not part of Croatia, the Croatians had announced to Serbia that they would be conducting the “cleanup” on Serbia’s territory, to keep it clean on their behalf.
We may only speculate about the reasons for carrying out this operation in such a heavy-handed, destructive way. One possibility is that allowing people to enter Liberland in the first place was a way for Croatia to lure some people to Liberland, become comfortable, and then come in and destroy everything to show everyone what would happen if they got involved in the project. Or perhaps it was the unexpected level of life, community-building, and construction going on in such a short period of time after the “opening of the border” that the Croatian police felt like they had to put a stop to it before things got so big they could not be easily destroyed anymore.
No matter the reasons, the raid had a chilling effect on prospective Liberlanders. Though there is plenty of video documentation of the operation, no one made a viral video about it this time. Though some media did pick up the news, it did not become a big story. Consequently, the PR fallout from this for Croatia was not unmanageable.
Liberlanders soon returned to the territory. However, the level of enthusiasm, energy, and external support was not as great as it had been before the raid. From then on, settlement efforts focused mainly on Liberty Island, unreachable by trucks and impossible for forestry workers to get to without a large boat which they seem not to have. Though perhaps a more strategic place to set up camp, Liberty Island is also much more prone to flooding than the rest of Liberland.
In the following few months, several makeshift houses were constructed using a combination of wood and sandbags. During this time, Liberland even hosted a first wedding on the island. The settlement was kept alive during winter as well, with Liberland enthusiasts staying mostly in houseboats whenever it was impossible to camp on site.
In the meantime, an enthusiastic settler couple bought a sizeable house with a courtyard in the village closest to Liberland – Zmajevac – which they have transformed into a base of operations for settlers. This is now called Liberbase and it is where visits to Liberland start, with bikes, supplies, and construction materials being gathered before going on the 40-minute bike ride.

In the spring of 2024, work started on the reconstruction of a former hunting lodge at a central location on Liberland’s mainland – Jefferson Square. The building was demolished a few years ago but the foundations, including a cellar, were left in place. The site was cleared, the foundations refreshed, and new walls for the future governmental building have sprung up from the ground. A professional construction crew was hired to speed up the re-building of this base, using large concrete bricks, to a standard that will make it logistically and practically difficult for the Croatian police and forestry workers to try to destroy.
 The battle for legitimacy
The battle for legitimacy The ongoing construction in Liberland is rather slow. It is difficult to bring construction materials to Liberland. It is prohibited to drive motor vehicles on the bike path leading to Liberland, which means that everything has to be manually hauled from Liberbase on cargo bikes. In addition, from time to time, bikes get stolen by the police or forestry workers. Despite these difficulties, the determination of the settlers is unwavering and they are working every day to move construction forward.
The ongoing construction in Liberland is rather slow. It is difficult to bring construction materials to Liberland. It is prohibited to drive motor vehicles on the bike path leading to Liberland, which means that everything has to be manually hauled from Liberbase on cargo bikes. In addition, from time to time, bikes get stolen by the police or forestry workers. Despite these difficulties, the determination of the settlers is unwavering and they are working every day to move construction forward.Is it possible to bring materials by boat? How did they get sandbags and other materials to Liberty Island?
The importance of such a commitment should not be underestimated. The continuous presence of settlers is incredibly important for Liberland. It shows the seriousness of the project. It shows that Liberland is a genuine community and a fledgling nation rather than, as some accusations tend to go, just an elaborate publicity stunt.
Practical difficulties with the Croatian authorities are not limited to construction-related issues. Even staying and camping in Liberland comes with its quirks. If you’re staying on Jefferson Square, you should be prepared for several police visits every day. These check-ups are usually nothing dramatic. The police usually show up, ask a couple of questions, and perhaps tell the settlers that they are not allowed to camp there or start a fire, but they don’t actually do anything more than that and just go about their day.
It seems that the Croatian police are rather shy about enforcing Croatian law in a territory that is not officially considered part of Croatia. International law often takes into account the de facto situation of the matter in any dispute. If Croatia enforced their law in Liberland, this would therefore be an indication that they do, in fact, consider the territory to be theirs in practice, despite the official stance of the state. It would play into the hands of Serbia, reinforcing their claims to the large parcels of land on the other side of the Danube.
In addition, Liberlanders on the ground report that the majority of Croatian police officers generally behave quite fairly and respectfully toward them – only a minority appear to hold a personal grudge against Liberland, being abusive and sometimes even violent instead. It seems highly likely that the police in general are just doing their job, following orders from above. Most of them don’t actually take it as a personal commitment to make life more difficult for the Liberlanders.
This is rather important from a big-picture perspective, because the settlers, by contrast, are often heavily personally invested in the project and see it as their mission to see Liberland develop into a proper country. This disparity in energy and determination is strong and perhaps this is what will, in the end, cause Liberland to prevail in this drawn-out dispute.

The dispute with Hrvatske šume is quite different. As of mid-2024, the forestry workers tend to turn up at Jefferson Square about every fortnight. Unlike the police, they do not limit themselves to words but tend to steal everything that is not bolted down – including tools, materials, tents, bikes, and personal possessions of the settlers camping there. The justification remains the same – to “clean the forest of any waste.” In their encounters with the police as well as the forestry workers, Liberlanders are of course meticulous in their video documentation of any illegal actions by the authorities.
The Liberlanders’ difficulties, however, do not just stay local. As previously mentioned, upon trying to enter Liberland from Croatia, people who do not have EU citizenship are promptly issued a one-to-three-month ban on entering Croatia, with 7 days to leave the country. This is done under legislation relating to citizenship and tourism.
However, things can escalate even further. Since last year, several key Liberland settlers and organizers, including Liberland’s President Vít Jedlička himself, have seen “heavier guns” used against them. They have been banned from entering Croatia for 5 years under anti-terrorism legislation, where the authorities argue that these Liberlanders are something akin to a threat to national security.
The Liberlanders have mounted a legal defense against this, in addition to challenging Croatia on other legal fronts. They have had some successes so far – in particular, it should now be clear that the Liberlanders do not need any building permits to construct buildings on their territory. Unfortunately, other issues – including the 5-year bans from Croatia – still remain unresolved.
Most Liberlanders remain hopeful nonetheless. They have seen their situation move forward significantly over the last year. A year ago, they were not even able to enter Liberland without being chased and/or arrested. Now, even some construction is possible, albeit in a limited way.
The road ahead
The long-term vision, of course, remains to build a full-fledged, internationally respected and recognized city-state. Liberland’s leaders often speak of a “Balkan Monaco”, referring to the amazing development possibilities that a freedom-oriented country in the middle of Europe could offer. Liberland has already hosted an urbanist/architectural contest, and there are concrete plans for the first hotel as well as a riverside real estate development. What is more, Liberland’s land is actually more than three times the size of Monaco.
Nevertheless, Liberland cannot move forward in a meaningful way toward these visions and aspirations under the status quo. The Liberlanders need to be able to build at scale and be free from harassment, both by the police and the forestry workers. Some kind of political deal is necessary as the next step toward proper development of Liberland.
Such a deal could take multiple forms, but all of them involve the Croatian authorities changing their attitude toward Liberland away from a policy of unrelenting obstruction – not necessarily toward outright recognition, but at least toward accepting Liberland as a neighborly project that will move forward and develop in some way.
One option could be to allow motor vehicles on the bike path toward Liberland, with a deal that could include charging Liberlanders some fair tolls to pay for the wear and tear of the pavement. An alternative would be to simply allow river crossing into Liberland from Serbia on the Danube. Since Croatia does not officially consider Liberland its territory, their current interference with this traffic is illegal anyway. Simply stopping this illegal conduct would help Liberland significantly without Croatia facilitating Liberland’s development in any active way.

Regardless of these options, the first and most notable step would be to stop banning non-EU citizens from re-entering Croatia as well as lift the existing (entirely unjustified and unreasonable) 5-year bans on Jedlička and the others.
It is easy to see why Croatia is wary and suspicious of Liberland’s development. One can understand the worries of a state in whose immediate proximity there is a new and unknown state growing and taking root. Nevertheless, Croatia actually has a lot to gain from making some kind of deal with Liberland.
First: currently there are perhaps a dozen policemen on patrol around Liberland at all times. This includes police vehicles and boats. This is a significant expense for the police force – an expense which is rather unsubstantiated, given that Liberlanders have clearly proven to be peaceful people who do not wish to pose any threat to Croatia, its people, or its law enforcement officers. Making a deal would mean that this large expense is not needed anymore.
Second: Liberland borders an area of Croatia that has been rather “left behind”, is underdeveloped, and suffers from a lack of jobs and investment. Consequently, younger people are leaving the area and the current population is growing older. If Liberland was growing and open for business nearby, it would provide the region exactly with the job opportunities, large investment, and overall development that it desperately needs.
Third: Croatia could use Liberland as an opportunity to actually gain an advantage in the ongoing border dispute with Serbia. As previously mentioned, Croatia cannot openly and properly administer the territory, as it would be an indication in the eyes of international law that they consider the territory to be theirs. On the other hand, it Liberland is located on “their” side of the Danube, so Croatia does have an interest in making sure the area is under their control somehow. Striking a deal with Liberland could involve Liberland agreeing to some obligations related to the administration of the territory which correspond to Croatia’s priorities. In this way, Croatia would have an active say in what happens on this land, effectively “outsourcing” its administration without officially claiming it as part of Croatia.
In addition to all these advantages being present, Liberland is very much open to cooperation with Croatia and is keenly looking forward to welcoming any future productive relations with Croatian authorities. There will be no grudges held on Liberland’s side, and if a mutually beneficial deal or solution were to be found, no one would look behind at any historical quibbles or difficulties. Liberland would be an excellent and friendly neighbor to Croatia, not just causing any issues but actively helping the overall development of the surrounding region.
Time will tell how things will develop. At the present, the momentum, energy, and enthusiasm is definitely on the side of Liberland. There seems to be very little actual interest from the Croatian side to cause issues for Liberland and to continue to prevent the fledgling state from developing further. All that is left are the bureaucratic hurdles of a state that is being overly conservative about its approach to the important issues of the day. Things might take time, but seeing the determination of the settlers and the willingness of all Liberlanders to be unrelenting in their fight for the cause, it is not difficult to argue that we might be seeing the dawn of Liberland as the world’s next proper city-state as we speak.
-
 @ 472f440f:5669301e
2024-12-03 05:11:52
@ 472f440f:5669301e
2024-12-03 05:11:52Uber seed investor and executive producer of the All In podcast Jason Calacanis has been publicly sounding the alarm bell about Microstrategy's bitcoin treasury strategy and the cheer leading exhibited by the company's CEO, Michael Saylor. Calacanis believes that Microstrategy's bitcoin acquisition techniques are a Ponzi scheme waiting to implode. Going as far as to question whether or not Microstrategy is the next FTX.
Earlier today, Jason spent a section of an episode of This Week in Startups to discuss his worries about MSTR's bitcoin treasury strategy, Saylor's overt pumping of the strategy, and the fact that there are other companies like Marathon Holdings beginning to deploy similar convertible debt strategies. While I can see how this can be unnerving for many, I do think there is a fundamental misunderstanding of what Microstrategy is doing. Last week I explained the strategy in a tweet, which I'll reiterate here:
Whether you like it or not, Saylor and Microstrategy have found a way to give pools of liquidity (particularly pools with mandates to allocate to fixed income) exposure to bitcoin’s volatility via convertible notes. The converts are performing better than any other fixed income product on the market.
Other investors have noticed this and have piled into MSTR as well understanding that demand for the converts will increase and enable Microstrategy to accumulate more bitcoin. Those investors feel comfortable with the premium to mNAV MSTR is trading at because they believe the demand for a high performing fixed income product will remain high and likely increase.
Microstrategy can continue doing this until viable competition comes to market because there is no one else offering this type of bitcoin return exposure to fixed income investors at scale. Another important detail, the convertible notes have a duration of 5 years or more while bitcoin’s lowest 4-year CAGR is 26% and its 50th percentile 4-year CAGR is 91%. If you think this will continue then this is a pretty safe bet for Microstrategy and the convertible note holders.
In a world were central banks and governments have gone mad with currency debasement and debt expansion it is pretty safe to assume that bitcoin adoption will not only continue but accelerate from here. What do I think about Microstrategy accumulating this much bitcoin? It makes me a bit uneasy but there’s nothing I can do to stop it and bitcoin will survive in the long run. Even if Microstrategy blows up somehow (I don’t think this is likely). Bitcoin was designed to be anti-fragile.
This is a classic case of “don’t hate the player, hate the game”. Or better yet, join the game. After all, the only winning move is to play.
Essentially, Michael Saylor is taking a long-term bet on bitcoin's continued adoption/monetization and trying to accumulate as much as possible by issuing convertible notes with a 4+ year duration, which should increase the likelihood that Microstrategy is in the black on their bitcoin buys over time as history has shown that anyone who holds bitcoin for more than four years has performed well. This should, in turn, be reflected in their stock price, which should increase alongside bitcoin and convert the debt they've accrued into newly issued shares of MSTR. Through the process, if the strategy is executed successfully, increasing the amount of bitcoin per share for MSTR shareholders. (This is the only metric shareholders should care about in my opinion.)
Yes, this may seem crazy to many and extremely risky to most, but that is the nature of free markets. Every company takes calculated risks in an attempt to increase shareholder value. Michael Saylor and company are betting on the fact that bitcoin will continue to be adopted and are utilizing pools of capital that don't have the ability to buy bitcoin directly, but want exposure to its volatility to achieve their goals. To me it looks like a perfectly symbiotic relationship. Microstrategy is able to accumulate more bitcoin and increase their bitcoin per share while fixed income investors are able to access a product that performs well above their benchmark due to the embedded volatility of the exposure to bitcoin Microstrategy provides.
This won't be a surprise to any of you freaks, but I think it's a pretty smart bet to make. Bitcoin is almost 16-years old. It has established itself as a reserve asset for individuals, companies and countries. A reserve asset that is completely detached from the whims of central planners, transparent, predictable, scarce, and can be transmitted over the Internet. Bitcoin is an idea whose time has come. And more people are beginning to recognize this.
This is one of the beautiful aspects of the public company convertible-note-to-bitcoin strategy that Microstrategy has deployed over the last few years. They are able to harness the benefits of forces that are external to their core business to provide shareholders with value. Michael Saylor could stop buying bitcoin tomorrow and it wouldn't affect bitcoin's adoption in the medium to long-term. He continues to buy bitcoin, and encourages others to do the same, because he recognizes this.
Bitcoin is the apex predator of treasury assets for every individual, company, non-profit or government. The assets competing to be treasury assets are all centrally controlled, easily manipulable, and quickly losing favor. Earlier today, Federal Reserve Board Governor Christopher Waller came out and admitted that inflation is kicking the Fed's ass. They cannot tame it.
Waller may posture by saying that "submission is inevitable", but that doesn't make it true. There is simply too much debt and not enough dollars. The annual interest expense on the US Federal debt is now larger than our spending on national defense. The Fed, whether it wants to admit it or not, is going to have to monetize that debt via the debasement of the dollar. If you are using dollars as a treasury asset it is very important that you understand this and react accordingly by adopting a bitcoin strategy. This is what Michael Saylor is trying to make his peers in public markets understand.
Sure, his marketing tactics may seem a bit uncouth to many and the way in which he's expressing his belief through Microstrategy's accumulation strategy may seem risky, but it's hard to argue that his core thesis is flawed. Especially when you consider the fact that bitcoin has officially climbed to the strata of being seriously considered as a treasury asset for the most powerful nation state in the world. I listen to the All In podcast quite frequently and genuinely like the show. It is a good way to gain perspective on how Silicon Valley investors view the world. If I were to give Jason any advice it would be to take a step back and to apply one of the most frequently discussed topics of the last on his show, the emergence of AI and the importance of everyone to incorporate AI into their businesses and workflows as quickly as possible before they get left behind. The same mental model applies to the emergence of bitcoin as a dominant reserve asset.
It is imperative that every individual, company and government adopts a bitcoin treasury strategy if they want to be able to succeed moving forward without the inherent resistance that is introduced from storing the fruit of your labor in a money or money-like asset that does not preserve purchasing power over time. Just because Saylor has recognized this, moved aggressively to effectuate his understanding via his company's balance sheet, and vociferously markets the strategy to others doesn't mean he's wrong. As I said in my tweet last week, I personally prefer to hold actual bitcoin. That doesn't mean that Microstrategy and others haven't honed in on something unique and legitimate given their circumstances and access to certain financial tools.
Final thought... I apologize for the extended hiatus. I hit a hard wall of writer's block over the last month. I think the time away from the keyboard has been good for me and the quality of this rag moving forward.
-
 @ 3b7fc823:e194354f
2025-02-10 17:34:18
@ 3b7fc823:e194354f
2025-02-10 17:34:18Dealing with law enforcement can be a challenging and stressful experience. However, understanding your rights and knowing how to navigate such situations can empower you to protect yourself. Here’s a structured approach to handle these interactions effectively:
- Stay Calm and Compliant:
-
When approached by law enforcement, remain calm and avoid sudden movements. Slowly raise your hands and identify yourself if possible.
-
Ask for Identification:
-
Request the officer's name, badge number, and station. This documentation can be crucial later on.
-
Know Your Miranda Rights:
-
Upon arrest, you have the right to remain silent. Do not answer questions without consulting a lawyer. If Mirandized, exercise your right to remain silent.
-
Refuse Incriminating Statements:
-
Avoid answering questions that could incriminate yourself. Politely state, "I will not answer any questions at this time."
-
Document the Incident:
-
Use your phone or notebook to record details such as dates, times, and descriptions of interactions. Note any injuries or mistreatment.
-
Seek Legal Advice:
-
After the encounter, contact a lawyer. They can review evidence and provide guidance on how to proceed.
-
Understand Search and Seizure Laws:
-
Officers generally need a warrant to search your property unless there's probable cause. If stopped without a warrant, calmly refuse entry.
-
Use a Body Camera Policy:
-
If applicable, ask for the officer's body camera footage and request it via formal complaint if refused.
-
Know When to Comply:
-
Comply with instructions that do not infringe on your rights, such as providing identification when legally required.
-
Consider a Witness Statement:
- If you witness illegal actions, consider reporting them. Your role as a bystander may be crucial in documenting incidents.
-
Seek Emotional Support:
- Interactions with law enforcement can be traumatic. Reach out to support groups or mental health resources for assistance.
-
Understand Legal Recourse:
- If rights are violated, consult legal aid societies or civil rights organizations for guidance on filing complaints or seeking redress.
Conclusion: Understanding your rights and documenting interactions is essential when dealing with law enforcement. This guide provides a framework to help you navigate such situations confidently and protect your rights effectively. Remember, knowledge is power, and being informed can lead to better outcomes in challenging circumstances.
Advocating for privacy does not finance itself. If you enjoyed this article, please consider zapping or sending monero
82XCDNK1Js8TethhpGLFPbVyKe25DxMUePad1rUn9z7V6QdCzxHEE7varvVh1VUidUhHVSA4atNU2BTpSNJLC1BqSvDajw1
-
 @ 6be5cc06:5259daf0
2025-01-21 23:17:29
@ 6be5cc06:5259daf0
2025-01-21 23:17:29A seguir, veja como instalar e configurar o Privoxy no Pop!_OS.
1. Instalar o Tor e o Privoxy
Abra o terminal e execute:
bash sudo apt update sudo apt install tor privoxyExplicação:
- Tor: Roteia o tráfego pela rede Tor.
- Privoxy: Proxy avançado que intermedia a conexão entre aplicativos e o Tor.
2. Configurar o Privoxy
Abra o arquivo de configuração do Privoxy:
bash sudo nano /etc/privoxy/configNavegue até a última linha (atalho:
Ctrl+/depoisCtrl+Vpara navegar diretamente até a última linha) e insira:bash forward-socks5 / 127.0.0.1:9050 .Isso faz com que o Privoxy envie todo o tráfego para o Tor através da porta 9050.
Salve (
CTRL+OeEnter) e feche (CTRL+X) o arquivo.
3. Iniciar o Tor e o Privoxy
Agora, inicie e habilite os serviços:
bash sudo systemctl start tor sudo systemctl start privoxy sudo systemctl enable tor sudo systemctl enable privoxyExplicação:
- start: Inicia os serviços.
- enable: Faz com que iniciem automaticamente ao ligar o PC.
4. Configurar o Navegador Firefox
Para usar a rede Tor com o Firefox:
- Abra o Firefox.
- Acesse Configurações → Configurar conexão.
- Selecione Configuração manual de proxy.
- Configure assim:
- Proxy HTTP:
127.0.0.1 - Porta:
8118(porta padrão do Privoxy) - Domínio SOCKS (v5):
127.0.0.1 - Porta:
9050
- Proxy HTTP:
- Marque a opção "Usar este proxy também em HTTPS".
- Clique em OK.
5. Verificar a Conexão com o Tor
Abra o navegador e acesse:
text https://check.torproject.org/Se aparecer a mensagem "Congratulations. This browser is configured to use Tor.", a configuração está correta.
Dicas Extras
- Privoxy pode ser ajustado para bloquear anúncios e rastreadores.
- Outros aplicativos também podem ser configurados para usar o Privoxy.
-
 @ 0fa80bd3:ea7325de
2025-01-30 04:28:30
@ 0fa80bd3:ea7325de
2025-01-30 04:28:30"Degeneration" or "Вырождение" ![[photo_2025-01-29 23.23.15.jpeg]]
A once-functional object, now eroded by time and human intervention, stripped of its original purpose. Layers of presence accumulate—marks, alterations, traces of intent—until the very essence is obscured. Restoration is paradoxical: to reclaim, one must erase. Yet erasure is an impossibility, for to remove these imprints is to deny the existence of those who shaped them.
The work stands as a meditation on entropy, memory, and the irreversible dialogue between creation and decay.
-
 @ 04ed2b8f:75be6756
2025-02-10 11:30:04
@ 04ed2b8f:75be6756
2025-02-10 11:30:04The world doesn’t care about your excuses. It doesn’t care about your past, your wounds, or the battles you’ve already fought. Life will not lower the weight just because you feel tired. You either rise, or you stay down.
But here’s the truth—you are not your past. You are not your failures, not your pain, not the things that tried to break you. You are what you choose to become.
Some people get knocked down and never get back up. Some let their past define them, cage them, strip them of their potential. And then there are those who decide. They decide that no matter what happened, they will rise. They will fight. They will carve their own path, even if they have to do it with their bare hands.
Your Past is a Weapon—If You Use It Right
Your past can be two things: a chain or a sword.
- Weak minds wear their past like a shackle, letting it hold them back.
- Warriors forge their past into steel, using it as a blade to cut through the future they want.Scars? They aren’t signs of weakness. They are proof that you survived. That you endured. And that you’re still standing. So stop letting your past dictate your future. Rip the pen from its hands and write your own damn story.
The Weak Surrender. The Strong Rebuild.
Life will try to break you. That’s a fact. You will lose, you will hurt, you will doubt. But none of that matters. The only thing that matters is what you do next.
- You can let failure drown you, or you can rise stronger.
- You can let heartbreak harden you, or you can sharpen yourself through it.
- You can let regret bury you, or you can burn it as fuel.
It’s easy to stay down. To blame the world. To say, “This is just who I am.” But warriors don’t do easy. They do necessary.
You Are the Architect of Your Own Power
Everything you need to win is already inside you. You don’t need permission. You don’t need the world to approve. You just need one thing: to choose.
- Choose discipline over comfort.
- Choose hunger over hesitation.
- Choose action over excuses.
- Choose to become something greater than your past.
Because in the end, that’s the only choice that matters.
The world will try to define you. It will try to chain you to your past, drag you down with doubt, and keep you in a box. Shatter it. Prove them wrong. Be the person that refuses to be shaped by circumstance—be the one who shapes themselves.
The past is done. The future is unwritten. The power to decide who you become? That’s all yours. Now get up and take it.
-
 @ 3b7fc823:e194354f
2025-02-10 13:13:25
@ 3b7fc823:e194354f
2025-02-10 13:13:25Alright, let’s get one thing straight: you’re scrolling through your phone, shopping online, maybe even working from home. But here’s the thing – someone might be watching. Not in the creepy stalker way, but in the “is that company really needing my data?” kind of way. That’s where a Virtual Private Network (VPN) comes in, saving you from the prying eyes of marketers, governments, and even your own internet provider.
What Does a VPN Do?
A VPN creates a secure, encrypted connection between your device and a VPN server. This allows you to browse the internet anonymously, keeping your online activities private from your Internet Service Provider (ISP), network administrators, and even hackers. When you connect to a VPN, your internet traffic is routed through an intermediary server, making it difficult for anyone to track your online movements.
Why You Need a VPN: Privacy edition
- Hiding Your IP Address
Every time you jump online, your device gets an IP address, like a digital ID. If you don’t use a VPN, everyone can see this ID, making it easy for advertisers and governments to track your every move.
-
[X ] Myth: A VPN hides my IP address from everyone.
-
[X] Reality: A VPN hides your IP address only from the websites you visit and your ISP. Your internet service provider still knows you're using a VPN, but they won't be able to see what sites you're visiting. Your VPN knows what sites you are visiting and may know who you are as well.
-
Bypassing Censorship
Ever tried accessing something that’s blocked in your country? A VPN can help you bypass those restrictions, letting you watch the latest shows, access social media, or even download books without getting flagged as a troublemaker.
- Protecting Your Data
When you connect to public Wi-Fi – like at a café or airport – you’re basically handing over your data on a silver platter. A VPN encrypts this data, so even if someone intercepts it, they can’t decode it. Think of it as adding an extra layer of security.
- Avoiding Surveillance
Companies and governments love collecting data. From what you search to who you talk to, there’s a lot of stuff that’s none of their business. A VPN ensures that only you know where you’ve been online.
- Safeguarding Your Personal and Professional Life
Whether you’re working from home or just shopping for a present, a VPN keeps your activities private. It’s like having a secure safe for all your online stuff, so no one can snoop.
- Stopping Targeted Ads
Companies track your browsing habits to send you ads that follow you around the internet. A VPN breaks this cycle, making sure those creepy “you might like” ads stop following you around.
- No Logs Policy
Some VPNs keep records of your activity, which means they could be handed over if the government comes knocking. But with a no-logs policy, nothing is stored – they promise ;)
- The Dark Side of Free VPNs
Before you jump into using a free VPN, think twice. Free services often come with a catch: they might sell your data to advertisers or even track your activity themselves. It’s like getting a free hotdog at a gas station – it sounds great, but you’ll probably regret it later.
How to Use a VPN (Because You’re Not a Tech Wizard)
- Choose the Right Provider
Go for a reputable service that offers strong encryption and a no-logs policy. Look for options with a kill switch, which stops any data from being leaked if the connection drops. I prefer ones you can pay annoymously but that may be overkill for most people.
- Download and Install
Once you pick a provider, download the app to your device. It’s not rocket science, but it does require a bit more than just opening an email.
- Set It Up
Most VPNs have user-friendly interfaces. Just click “Connect” and you’re good to go. You might need to enter your login details or use a password from your provider.
The Final Word Using a VPN isn’t about being a hacker or someone with something to hide. It’s about respecting your privacy and having control over what you share online. In today’s world, where companies and governments are constantly getting more creative about how they collect data, it’s practically a requirement if you want to stay ahead of the curve.
So there you have it – the secret life of your internet. With a VPN, you’re not just protecting yourself; you’re making sure that your digital footprint is as small as possible. Whether you’re at home or on the go, a VPN gives you the freedom to surf, shop, and work without anyone watching your every move.
And hey, if you’re still not convinced, just think about it this way: imagine your internet connection as a crowded public space. Without a VPN, everyone’s staring at you. With one, you’re wearing a mask, and no one’s the wiser.
Advocating for privacy does not finance itself. If you enjoyed this article, please consider zapping or sending monero
82XCDNK1Js8TethhpGLFPbVyKe25DxMUePad1rUn9z7V6QdCzxHEE7varvVh1VUidUhHVSA4atNU2BTpSNJLC1BqSvDajw1
-
 @ a849beb6:b327e6d2
2024-11-23 15:03:47
@ a849beb6:b327e6d2
2024-11-23 15:03:47
\ \ It was another historic week for both bitcoin and the Ten31 portfolio, as the world’s oldest, largest, most battle-tested cryptocurrency climbed to new all-time highs each day to close out the week just shy of the $100,000 mark. Along the way, bitcoin continued to accumulate institutional and regulatory wins, including the much-anticipated approval and launch of spot bitcoin ETF options and the appointment of several additional pro-bitcoin Presidential cabinet officials. The timing for this momentum was poetic, as this week marked the second anniversary of the pico-bottom of the 2022 bear market, a level that bitcoin has now hurdled to the tune of more than 6x despite the litany of bitcoin obituaries published at the time. The entirety of 2024 and especially the past month have further cemented our view that bitcoin is rapidly gaining a sense of legitimacy among institutions, fiduciaries, and governments, and we remain optimistic that this trend is set to accelerate even more into 2025.
Several Ten31 portfolio companies made exciting announcements this week that should serve to further entrench bitcoin’s institutional adoption. AnchorWatch, a first of its kind bitcoin insurance provider offering 1:1 coverage with its innovative use of bitcoin’s native properties, announced it has been designated a Lloyd’s of London Coverholder, giving the company unique, blue-chip status as it begins to write bitcoin insurance policies of up to $100 million per policy starting next month. Meanwhile, Battery Finance Founder and CEO Andrew Hohns appeared on CNBC to delve into the launch of Battery’s pioneering private credit strategy which fuses bitcoin and conventional tangible assets in a dual-collateralized structure that offers a compelling risk/return profile to both lenders and borrowers. Both companies are clearing a path for substantially greater bitcoin adoption in massive, untapped pools of capital, and Ten31 is proud to have served as lead investor for AnchorWatch’s Seed round and as exclusive capital partner for Battery.
As the world’s largest investor focused entirely on bitcoin, Ten31 has deployed nearly $150 million across two funds into more than 30 of the most promising and innovative companies in the ecosystem like AnchorWatch and Battery, and we expect 2025 to be the best year yet for both bitcoin and our portfolio. Ten31 will hold a first close for its third fund at the end of this year, and investors in that close will benefit from attractive incentives and a strong initial portfolio. Visit ten31.vc/funds to learn more and get in touch to discuss participating.\ \ Portfolio Company Spotlight
Primal is a first of its kind application for the Nostr protocol that combines a client, caching service, analytics tools, and more to address several unmet needs in the nascent Nostr ecosystem. Through the combination of its sleek client application and its caching service (built on a completely open source stack), Primal seeks to offer an end-user experience as smooth and easy as that of legacy social media platforms like Twitter and eventually many other applications, unlocking the vast potential of Nostr for the next billion people. Primal also offers an integrated wallet (powered by Strike BLACK) that substantially reduces onboarding and UX frictions for both Nostr and the lightning network while highlighting bitcoin’s unique power as internet-native, open-source money.
Selected Portfolio News
AnchorWatch announced it has achieved Llody’s Coverholder status, allowing the company to provide unique 1:1 bitcoin insurance offerings starting in December.\ \ Battery Finance Founder and CEO Andrew Hohns appeared on CNBC to delve into the company’s unique bitcoin-backed private credit strategy.
Primal launched version 2.0, a landmark update that adds a feed marketplace, robust advanced search capabilities, premium-tier offerings, and many more new features.
Debifi launched its new iOS app for Apple users seeking non-custodial bitcoin-collateralized loans.
Media
Strike Founder and CEO Jack Mallers joined Bloomberg TV to discuss the strong volumes the company has seen over the past year and the potential for a US bitcoin strategic reserve.
Primal Founder and CEO Miljan Braticevic joined The Bitcoin Podcast to discuss the rollout of Primal 2.0 and the future of Nostr.
Ten31 Managing Partner Marty Bent appeared on BlazeTV to discuss recent changes in the regulatory environment for bitcoin.
Zaprite published a customer testimonial video highlighting the popularity of its offerings across the bitcoin ecosystem.
Market Updates
Continuing its recent momentum, bitcoin reached another new all-time high this week, clocking in just below $100,000 on Friday. Bitcoin has now reached a market cap of nearly $2 trillion, putting it within 3% of the market caps of Amazon and Google.
After receiving SEC and CFTC approval over the past month, long-awaited options on spot bitcoin ETFs were fully approved and launched this week. These options should help further expand bitcoin’s institutional liquidity profile, with potentially significant implications for price action over time.
The new derivatives showed strong performance out of the gate, with volumes on options for BlackRock’s IBIT reaching nearly $2 billion on just the first day of trading despite surprisingly tight position limits for the vehicles.
Meanwhile, the underlying spot bitcoin ETF complex had yet another banner week, pulling in $3.4 billion in net inflows.
New reports suggested President-elect Donald Trump’s social media company is in advanced talks to acquire crypto trading platform Bakkt, potentially the latest indication of the incoming administration’s stance toward the broader “crypto” ecosystem.
On the macro front, US housing starts declined M/M again in October on persistently high mortgage rates and weather impacts. The metric remains well below pre-COVID levels.
Pockets of the US commercial real estate market remain challenged, as the CEO of large Florida developer Related indicated that developers need further rate cuts “badly” to maintain project viability.
US Manufacturing PMI increased slightly M/M, but has now been in contraction territory (<50) for well over two years.
The latest iteration of the University of Michigan’s popular consumer sentiment survey ticked up following this month’s election results, though so did five-year inflation expectations, which now sit comfortably north of 3%.
Regulatory Update
After weeks of speculation, the incoming Trump administration appointed hedge fund manager Scott Bessent to head up the US Treasury. Like many of Trump’s cabinet selections so far, Bessent has been a public advocate for bitcoin.
Trump also appointed Cantor Fitzgerald CEO Howard Lutnick – another outspoken bitcoin bull – as Secretary of the Commerce Department.
Meanwhile, the Trump team is reportedly considering creating a new “crypto czar” role to sit within the administration. While it’s unclear at this point what that role would entail, one report indicated that the administration’s broader “crypto council” is expected to move forward with plans for a strategic bitcoin reserve.
Various government lawyers suggested this week that the Trump administration is likely to be less aggressive in seeking adversarial enforcement actions against bitcoin and “crypto” in general, as regulatory bodies appear poised to shift resources and focus elsewhere.
Other updates from the regulatory apparatus were also directionally positive for bitcoin, most notably FDIC Chairman Martin Gruenberg’s confirmation that he plans to resign from his post at the end of President Biden’s term.
Many critics have alleged Gruenberg was an architect of “Operation Chokepoint 2.0,” which has created banking headwinds for bitcoin companies over the past several years, so a change of leadership at the department is likely yet another positive for the space.
SEC Chairman Gary Gensler also officially announced he plans to resign at the start of the new administration. Gensler has been the target of much ire from the broader “crypto” space, though we expect many projects outside bitcoin may continue to struggle with questions around the Howey Test.
Overseas, a Chinese court ruled that it is not illegal for individuals to hold cryptocurrency, even though the country is still ostensibly enforcing a ban on crypto transactions.
Noteworthy
The incoming CEO of Charles Schwab – which administers over $9 trillion in client assets – suggested the platform is preparing to “get into” spot bitcoin offerings and that he “feels silly” for having waited this long. As this attitude becomes more common among traditional finance players, we continue to believe that the number of acquirers coming to market for bitcoin infrastructure capabilities will far outstrip the number of available high quality assets.
BlackRock’s 2025 Thematic Outlook notes a “renewed sense of optimism” on bitcoin among the asset manager’s client base due to macro tailwinds and the improving regulatory environment. Elsewhere, BlackRock’s head of digital assets indicated the firm does not view bitcoin as a “risk-on” asset.
MicroStrategy, which was a sub-$1 billion market cap company less than five years ago, briefly breached a $100 billion equity value this week as it continues to aggressively acquire bitcoin. The company now holds nearly 350,000 bitcoin on its balance sheet.
Notably, Allianz SE, Germany’s largest insurer, spoke for 25% of MicroStrategy’s latest $3 billion convertible note offering this week, suggesting growing appetite for bitcoin proxy exposure among more restricted pools of capital.
The ongoing meltdown of fintech middleware provider Synapse has left tens of thousands of customers with nearly 100% deposit haircuts as hundreds of millions in funds remain missing, the latest unfortunate case study in the fragility of much of the US’s legacy banking stack.
Travel
-
BitcoinMENA, Dec 9-10
-
Nashville BitDevs, Dec 10
-
Austin BitDevs, Dec 19
-
-
 @ c631e267:c2b78d3e
2025-01-18 09:34:51
@ c631e267:c2b78d3e
2025-01-18 09:34:51Die grauenvollste Aussicht ist die der Technokratie – \ einer kontrollierenden Herrschaft, \ die durch verstümmelte und verstümmelnde Geister ausgeübt wird. \ Ernst Jünger
«Davos ist nicht mehr sexy», das Weltwirtschaftsforum (WEF) mache Davos kaputt, diese Aussagen eines Einheimischen las ich kürzlich in der Handelszeitung. Während sich einige vor Ort enorm an der «teuersten Gewerbeausstellung der Welt» bereicherten, würden die negativen Begleiterscheinungen wie Wohnungsnot und Niedergang der lokalen Wirtschaft immer deutlicher.
Nächsten Montag beginnt in dem Schweizer Bergdorf erneut ein Jahrestreffen dieses elitären Clubs der Konzerne, bei dem man mit hochrangigen Politikern aus aller Welt und ausgewählten Vertretern der Systemmedien zusammenhocken wird. Wie bereits in den vergangenen vier Jahren wird die Präsidentin der EU-Kommission, Ursula von der Leyen, in Begleitung von Klaus Schwab ihre Grundsatzansprache halten.
Der deutsche WEF-Gründer hatte bei dieser Gelegenheit immer höchst lobende Worte für seine Landsmännin: 2021 erklärte er sich «stolz, dass Europa wieder unter Ihrer Führung steht» und 2022 fand er es bemerkenswert, was sie erreicht habe angesichts des «erstaunlichen Wandels», den die Welt in den vorangegangenen zwei Jahren erlebt habe; es gebe nun einen «neuen europäischen Geist».
Von der Leyens Handeln während der sogenannten Corona-«Pandemie» lobte Schwab damals bereits ebenso, wie es diese Woche das Karlspreis-Direktorium tat, als man der Beschuldigten im Fall Pfizergate die diesjährige internationale Auszeichnung «für Verdienste um die europäische Einigung» verlieh. Außerdem habe sie die EU nicht nur gegen den «Aggressor Russland», sondern auch gegen die «innere Bedrohung durch Rassisten und Demagogen» sowie gegen den Klimawandel verteidigt.
Jene Herausforderungen durch «Krisen epochalen Ausmaßes» werden indes aus dem Umfeld des WEF nicht nur herbeigeredet – wie man alljährlich zur Zeit des Davoser Treffens im Global Risks Report nachlesen kann, der zusammen mit dem Versicherungskonzern Zurich erstellt wird. Seit die Globalisten 2020/21 in der Praxis gesehen haben, wie gut eine konzertierte und konsequente Angst-Kampagne funktionieren kann, geht es Schlag auf Schlag. Sie setzen alles daran, Schwabs goldenes Zeitfenster des «Great Reset» zu nutzen.
Ziel dieses «großen Umbruchs» ist die totale Kontrolle der Technokraten über die Menschen unter dem Deckmantel einer globalen Gesundheitsfürsorge. Wie aber könnte man so etwas erreichen? Ein Mittel dazu ist die «kreative Zerstörung». Weitere unabdingbare Werkzeug sind die Einbindung, ja Gleichschaltung der Medien und der Justiz.
Ein «Great Mental Reset» sei die Voraussetzung dafür, dass ein Großteil der Menschen Einschränkungen und Manipulationen wie durch die Corona-Maßnahmen praktisch kritik- und widerstandslos hinnehme, sagt der Mediziner und Molekulargenetiker Michael Nehls. Er meint damit eine regelrechte Umprogrammierung des Gehirns, wodurch nach und nach unsere Individualität und unser soziales Bewusstsein eliminiert und durch unreflektierten Konformismus ersetzt werden.
Der aktuelle Zustand unserer Gesellschaften ist auch für den Schweizer Rechtsanwalt Philipp Kruse alarmierend. Durch den Umgang mit der «Pandemie» sieht er die Grundlagen von Recht und Vernunft erschüttert, die Rechtsstaatlichkeit stehe auf dem Prüfstand. Seiner dringenden Mahnung an alle Bürger, die Prinzipien von Recht und Freiheit zu verteidigen, kann ich mich nur anschließen.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 472f440f:5669301e
2024-11-05 04:24:47
@ 472f440f:5669301e
2024-11-05 04:24:47All eyes are, unsurprisingly, on the US Presidential election. Tomorrow is the big day. I don't want to come off as preachy, however it is pretty clear to me that if you are an American citizen who cares about bitcoin and would like to live under an administration that is eager to embrace the industry as opposed to an administration that is actively hostile toward bitcoin there is only one candidate who deserves your vote; Donald J. Trump. I think he's a better candidate for other reasons, but if you've read this rag for long enough you probably already know what those are. Instead of writing a screed about why I am voting for Trump, let's highlight some things outside of the election that you should be paying attention to this week.
First up, there are two Treasury auctions; $42B of 10-Year notes tomorrow and $25B 30-Year bonds on Wednesday.
It will be interesting to see what the demand for these auctions is and how they affect rates. The long end of the yield curve has been pumping since the Fed's rate cut in the middle of September, which is the market signaling that it does not believe inflation has been appropriately tamed. Yields came down today, but as you can see from the charts things are trending in the wrong direction.
As the Treasury issues new debt at higher rates, the interest expense on that debt, naturally, drifts higher. If the long end of the yield curve doesn't come down aggressively over the course of the next year this is going to be a big problem. There are trillions of dollars worth of Treasury debt that needs the be rolled over in the next few years and it would be advantageous for the Treasury if that debt wasn't being rolled over with yields as high as they are. With the amount of debt the country has accrued in recent decades, every incremental dollar of debt that gets issued and/or rolled over at higher interest rates exacerbates the problem. We are approaching the territory of runaway exponentials, as evidenced by this chart. The growth slope gets steeper and steeper
This debt problem is the elephant in the room that needs to be addressed as quickly as possible. The national debt hit $1.2T in early 1983. It then took 26 years to 10x from $1.2T to $12T in late 2009 and has only taken another 15 years to triple from there to $36T or 30x from the arbitrary base I picked out (Q1 1983).
With this in mind, keep an eye out for these auctions tomorrow and Wednesday, where rates end at the end of trading on Wednesday, and whether or not we officially push over $36T. Regardless of who wins the election tomorrow, this is a problem that needs to be confronted. Whether or not it can be solved at all is up for debate. I don't see how what can be done to reel in this runaway train at this point. However, at the very least, we should acknowledge that we're in the realm of exponentials and have people prepare accordingly by accumulating hard assets that cannot be debased (bitcoin).
The other thing to pay attention to is the FOMC meeting on Wednesday and the announcement of the results of the meeting on Thursday. Will Jerome and the other Fed board members to keep rates where they are, cut, or raise rates? Raising rates seems to be out of the question despite the fact that many believe it would be the most prudent move considering how the long end of the yield curve reacted to the 50bps cut in September. If they decide to cut rates, by how much will they cut them? Will they slow the pace with a 25bps cut or continue at the 50bps clip established in September?
We'll find toward the end of this week. Don't lose sight of these events while the world is enthralled with the elections in the US.
I don't know about you freaks, but I couldn't feel more fortunate that bitcoin exists at a time like this. Having access to a distributed peer-to-peer digital cash system with a fixed supply during a time of incredible political divisiveness and out-of-control runaway sovereign debt feels like a Godsend.
Stay sane out there.
Final thought...
We're going to win.
-
 @ 0fa80bd3:ea7325de
2025-01-29 15:43:42
@ 0fa80bd3:ea7325de
2025-01-29 15:43:42Lyn Alden - биткойн евангелист или евангелистка, я пока не понял
npub1a2cww4kn9wqte4ry70vyfwqyqvpswksna27rtxd8vty6c74era8sdcw83aThomas Pacchia - PubKey owner - X - @tpacchia
npub1xy6exlg37pw84cpyj05c2pdgv86hr25cxn0g7aa8g8a6v97mhduqeuhgplcalvadev - Shopstr
npub16dhgpql60vmd4mnydjut87vla23a38j689jssaqlqqlzrtqtd0kqex0nkqCalle - Cashu founder
npub12rv5lskctqxxs2c8rf2zlzc7xx3qpvzs3w4etgemauy9thegr43sf485vgДжек Дорси
npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m21 ideas
npub1lm3f47nzyf0rjp6fsl4qlnkmzed4uj4h2gnf2vhe3l3mrj85vqks6z3c7lМного адресов. Хз кто надо сортировать
https://github.com/aitechguy/nostr-address-bookФиатДжеф - создатель Ностр - https://github.com/fiatjaf
npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6EVAN KALOUDIS Zues wallet
npub19kv88vjm7tw6v9qksn2y6h4hdt6e79nh3zjcud36k9n3lmlwsleqwte2qdПрограммер Коди https://github.com/CodyTseng/nostr-relay
npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wlAnna Chekhovich - Managing Bitcoin at The Anti-Corruption Foundation https://x.com/AnyaChekhovich
npub1y2st7rp54277hyd2usw6shy3kxprnmpvhkezmldp7vhl7hp920aq9cfyr7 -
 @ c4551bf3:f041d130
2025-02-10 08:21:56
@ c4551bf3:f041d130
2025-02-10 08:21:56TA88 là một nền tảng kỹ thuật số tiên tiến, mang đến trải nghiệm trực tuyến mượt mà và ổn định cho người dùng. Với giao diện thân thiện và thiết kế tối ưu, TA88 giúp người dùng dễ dàng truy cập trên cả máy tính và thiết bị di động. Nền tảng này được xây dựng trên công nghệ hiện đại, đảm bảo tốc độ xử lý nhanh, kết nối ổn định và khả năng tương thích cao, mang đến sự tiện lợi và linh hoạt tối đa cho người dùng.
Không ngừng đổi mới, TA88 liên tục cập nhật và nâng cấp hệ thống để mang đến chất lượng dịch vụ tốt nhất. Nền tảng này tích hợp nhiều công nghệ tiên tiến, giúp tối ưu hóa hiệu suất và nâng cao trải nghiệm người dùng. Nhờ vào sự cải tiến không ngừng, TA88 mang đến không gian giải trí phong phú, hấp dẫn và luôn bắt kịp xu hướng công nghệ, giúp người dùng có những trải nghiệm mới mẻ và thú vị.
Bên cạnh việc tập trung vào công nghệ, TA88 cũng đặc biệt chú trọng đến bảo mật và quyền riêng tư. Hệ thống bảo mật đa lớp với các giao thức mã hóa tiên tiến giúp bảo vệ dữ liệu cá nhân của người dùng một cách an toàn tuyệt đối. Việc áp dụng các biện pháp bảo mật nghiêm ngặt giúp TA88 đảm bảo môi trường trực tuyến an toàn, giúp người dùng yên tâm tận hưởng những tiện ích mà nền tảng mang lại.
Không chỉ tập trung vào công nghệ hiện đại, TA88 còn đầu tư mạnh mẽ vào dịch vụ chăm sóc khách hàng. Đội ngũ hỗ trợ chuyên nghiệp luôn sẵn sàng giải đáp mọi thắc mắc và cung cấp sự trợ giúp nhanh chóng, đảm bảo người dùng có trải nghiệm thuận tiện và hài lòng nhất. Sự tận tâm và chuyên nghiệp trong dịch vụ khách hàng là yếu tố giúp TA88 xây dựng lòng tin và sự trung thành từ cộng đồng người dùng.
Với những ưu điểm vượt trội, TA88 không ngừng đổi mới và phát triển để mang đến những trải nghiệm tối ưu. Nền tảng này liên tục cập nhật công nghệ, mở rộng tính năng và tối ưu hóa dịch vụ nhằm duy trì vị thế hàng đầu trong lĩnh vực giải trí kỹ thuật số. Nhờ vào sự kết hợp giữa công nghệ hiện đại, tính bảo mật cao và dịch vụ chuyên nghiệp, TA88 đã trở thành một trong những lựa chọn hàng đầu cho những ai tìm kiếm một nền tảng trực tuyến tiện lợi, an toàn và đáng tin cậy.
-
 @ c4551bf3:f041d130
2025-02-10 08:20:56
@ c4551bf3:f041d130
2025-02-10 08:20:56333Win là một nền tảng kỹ thuật số tiên tiến, mang đến trải nghiệm trực tuyến mượt mà và ổn định cho người dùng. Với giao diện thân thiện và thiết kế tối ưu, 333Win giúp người dùng dễ dàng truy cập trên cả máy tính và thiết bị di động. Hệ thống được xây dựng trên nền tảng công nghệ hiện đại, đảm bảo tốc độ xử lý nhanh, kết nối ổn định và hiệu suất tối ưu, giúp người dùng có những trải nghiệm liền mạch, tiện lợi mọi lúc, mọi nơi.
Không ngừng đổi mới, 333WIN liên tục cập nhật và nâng cấp hệ thống nhằm mang đến chất lượng dịch vụ tốt nhất. Nền tảng này tích hợp nhiều công nghệ tiên tiến để tối ưu hóa hiệu suất, giúp nâng cao sự tiện lợi và linh hoạt trong quá trình sử dụng. Nhờ vào sự cải tiến không ngừng, 333Win tạo ra một không gian giải trí phong phú, hấp dẫn và phù hợp với nhu cầu đa dạng, giúp người dùng luôn có những trải nghiệm trọn vẹn và mới mẻ.
Bên cạnh công nghệ tiên tiến, 333Win cũng đặc biệt chú trọng đến bảo mật và quyền riêng tư. Hệ thống bảo mật đa lớp với các giao thức mã hóa tiên tiến giúp bảo vệ dữ liệu cá nhân của người dùng một cách an toàn tuyệt đối. Việc áp dụng các biện pháp bảo vệ nghiêm ngặt giúp 333Win đảm bảo môi trường trực tuyến an toàn, giúp người dùng yên tâm tận hưởng những tiện ích mà nền tảng mang lại.
Không chỉ tập trung vào công nghệ hiện đại, 333Win còn chú trọng đến chất lượng dịch vụ chăm sóc khách hàng. Đội ngũ hỗ trợ chuyên nghiệp luôn sẵn sàng giải đáp thắc mắc và cung cấp sự trợ giúp nhanh chóng, đảm bảo trải nghiệm người dùng luôn thuận tiện và hài lòng. Sự tận tâm và chuyên nghiệp trong dịch vụ là yếu tố giúp 333Win xây dựng lòng tin và sự trung thành từ cộng đồng người dùng.
Với những ưu điểm vượt trội, 333Win không ngừng đổi mới và phát triển để mang đến những trải nghiệm tốt nhất. Nền tảng này liên tục cập nhật công nghệ, mở rộng tính năng và tối ưu hóa dịch vụ nhằm duy trì vị thế hàng đầu trong lĩnh vực giải trí kỹ thuật số. Nhờ vào sự kết hợp giữa công nghệ hiện đại, tính bảo mật cao và dịch vụ chuyên nghiệp, 333Win đã trở thành một trong những lựa chọn hàng đầu cho những ai tìm kiếm một nền tảng trực tuyến tiện lợi, an toàn và đáng tin cậy.
-
 @ 472f440f:5669301e
2024-10-16 01:57:41
@ 472f440f:5669301e
2024-10-16 01:57:41Over the last four years bitcoin has, among other things, established itself as an incredible corporate treasury asset that benefits those who adopt it as such. Microstrategy is the shining example of this theme going from a company that was hovering barely above a ~$1B market cap in mid-2020 to a ~$40B market cap company holding more than 1% of the 21,000,000 bitcoin that will ever exist. Microstrategy's success has emboldened a number of other publicly trader companies to follow suit. Bitcoin as a corporate treasury asset is well on its way to becoming a standard. If you run a business that doesn't hold bitcoin on its balance sheet you are doing yourself, your customers and your shareholders a disservice.
This is a trend that has its legs under it and will accelerate moving forward. A trend that I believe will emerge this cycle is incorporating bitcoin into real estate markets. Leon Wankum has been beating the drum about this for the last few years and I had the pleasure of sitting down with him this morning to record an episode of TFTC that will be published tomorrow morning. Leon is a real estate developer in Germany and he has made it his mission to educate and warn others in real estate about the demonetization of real estate that is under way due to the fact that bitcoin exists and it provides a far superior alternative.
These are pretty stark numbers. Nothing highlights the superior monetary properties of bitcoin better than looking at a chart of the average price of a home priced in USD v. bitcoin.
Since 2016: +46% in USD -99% in BTC
Since 2020: +34% in USD -70% in BTC
The funny thing is that an overwhelming majority of the individuals who make their living in real estate markets do not understand that this is happening to them. Many think they are doing exceptionally well all things considered. Sure, there may be a bit of a slow down and price retraction due to a couple of years of relatively elevated interest rates, but don't worry! The Fed is lowering rates again and the good times are about to start back up. Nothing could be further from the truth. This trend is going to continue unabated until bitcoin is fully monetized and those is the real estate industry, particularly real estate developers and those who lend capital to developers, should seriously take the time to understand what is happening to them.
Real estate is the largest store of value asset in the world at the moment. The most common number that is thrown around for the total size of the market is $300 TRILLION. $300 TRILLION of wealth being stored in an asset that is illiquid, comes with maintenance costs, taxes, insurance premiums, and susceptible to extreme weather event, among other things. Compared to bitcoin - which is extremely liquid, saleable, divisible and hard to confiscate, real estate is a far superior asset to store your wealth in. This is something that I'm sure is well understood by many of you reading this letter.
What's less understood is the dynamics of the real estate development market over the last few years, which have been severely hindered by elevated interest rates. The higher interest rate environment coupled with the inflationary pressures that forced rates higher in the first place have put developers in a predicament; they have a higher cost of capital to start new projects with raw material prices that are still much higher than they were before the economic lock downs of 2020-2022. This has led to a scenario where it isn't advantageous to start new projects and the projects that broke ground in 2021-2023 are finding that they need to incur more debt to get their developments across the finish line.
Despite the fact that interest rates are on their way back down, it doesn't seem like the economics of these projects are going to materially improve in the short to medium-term as headline inflation begins to creep back up. Couple this with the fact that the jobs market is cratering while real wages struggle to keep up with inflation and many builders are going to find themselves in a situation where they do actually complete a development problem but their cash flow suffers because their customers can't afford the inflated rents that builders will have to charge to get a return on their outlaid capital. Many will be put in a situation where they are forced to be happy with lower rents (cash flow) or sit on the sidelines making no cash flow.
The post-1971 era that brought with it a booming real estate industry is suffering the same fate as the bond market; the generation bull market is over. Real estate prices may go up, but that will be nothing more than a mirage of wealth creation. The unit of account those prices are built on is in dollars, which are being debased at an accelerating rate. Developers, banks and borrowers need to de-risk their real estate exposure and, as Leon points out, bitcoin is the only way to do this in an effective way.
Moving forward developers will have to finance by dual collateralizing their debt with the real estate and bitcoin. In the graphic below Leon illustrates what this type of financing structure will look like. Instead of taking $10m of debt to finance a project and putting it all into materials, construction and marketing, a developer will take out a $10m loan, put $1m in bitcoin and the rest toward the development project. Over the course of the construction of the real estate project, bitcoin will sit in the credit structure and, if held for 4+ years, should increase significantly in value. Saving the builder from risk of default and providing him some optionality in terms of what he can do with the project once it's finished.
In this scenario downside risk is contained - a developer isn't pouring all of the cash into bitcoin at the beginning so the worst case scenario is that bitcoin goes to zero (highly unlikely) and they can eat the small loss and hope to make up with it via cash flows once a project is finished, while upside potential is enormous. Bitcoin is still monetizing and having exposure to the hardest monetary asset the world has ever while it's monetizing has proven to be massively beneficial.
We are still in the early days of bitcoin and this idea will likely seem absolutely insane to most Tradfi investors, but I strongly believe that developers, banks and end consumers who don't leverage this type of bitcoin structured credit will be cooked in the long-run. And those that take advantage of this type of structure first will be considered geniuses in 20 years.
There are many more nuanced benefits to this strategy; holding bitcoin allows landlords and management companies to weather ongoing maintenance costs throughout the years, those who take out mortgages dual collateralized with a house and bitcoin not only protect the equity value of their property but could see their equity values increase significantly more than others using vanilla mortgages, and builders who accumulate bitcoin in their treasuries will be able to use better raw materials when building, which leads to more valuable properties that cash flow for longer.
Again, it's going to take time for these types of structures to become commonplace in the market, but I firmly believe this cycle will be the cycle that these strategies get off the ground. In four to five years they will have a track record and after that it will be considered irresponsible not to finance real estate in this way. The banks will begin to demand it.
Final thought... Sinus congestion sucks.
-
 @ c631e267:c2b78d3e
2024-10-23 20:26:10
@ c631e267:c2b78d3e
2024-10-23 20:26:10Herzlichen Glückwunsch zum dritten Geburtstag, liebe Denk Bar! Wieso zum dritten? Das war doch 2022 und jetzt sind wir im Jahr 2024, oder? Ja, das ist schon richtig, aber bei Geburtstagen erinnere ich mich immer auch an meinen Vater, und der behauptete oft, der erste sei ja schließlich der Tag der Geburt selber und den müsse man natürlich mitzählen. Wo er recht hat, hat er nunmal recht. Konsequenterweise wird also heute dieser Blog an seinem dritten Geburtstag zwei Jahre alt.
Das ist ein Grund zum Feiern, wie ich finde. Einerseits ganz einfach, weil es dafür gar nicht genug Gründe geben kann. «Das Leben sind zwei Tage», lautet ein gängiger Ausdruck hier in Andalusien. In der Tat könnte es so sein, auch wenn wir uns im Alltag oft genug von der Routine vereinnahmen lassen.
Seit dem Start der Denk Bar vor zwei Jahren ist unglaublich viel passiert. Ebenso wie die zweieinhalb Jahre davor, und all jenes war letztlich auch der Auslöser dafür, dass ich begann, öffentlich zu schreiben. Damals notierte ich:
«Seit einigen Jahren erscheint unser öffentliches Umfeld immer fragwürdiger, widersprüchlicher und manchmal schier unglaublich - jede Menge Anlass für eigene Recherchen und Gedanken, ganz einfach mit einer Portion gesundem Menschenverstand.»
Wir erleben den sogenannten «großen Umbruch», einen globalen Coup, den skrupellose Egoisten clever eingefädelt haben und seit ein paar Jahren knallhart – aber nett verpackt – durchziehen, um buchstäblich alles nach ihrem Gusto umzukrempeln. Die Gelegenheit ist ja angeblich günstig und muss genutzt werden.
Nie hätte ich mir träumen lassen, dass ich so etwas jemals miterleben müsste. Die Bosheit, mit der ganz offensichtlich gegen die eigene Bevölkerung gearbeitet wird, war früher für mich unvorstellbar. Mein (Rest-) Vertrauen in alle möglichen Bereiche wie Politik, Wissenschaft, Justiz, Medien oder Kirche ist praktisch komplett zerstört. Einen «inneren Totalschaden» hatte ich mal für unsere Gesellschaften diagnostiziert.
Was mich vielleicht am meisten erschreckt, ist zum einen das Niveau der Gleichschaltung, das weltweit erreicht werden konnte, und zum anderen die praktisch totale Spaltung der Gesellschaft. Haben wir das tatsächlich mit uns machen lassen?? Unfassbar! Aber das Werkzeug «Angst» ist sehr mächtig und funktioniert bis heute.
Zum Glück passieren auch positive Dinge und neue Perspektiven öffnen sich. Für viele Menschen waren und sind die Entwicklungen der letzten Jahre ein Augenöffner. Sie sehen «Querdenken» als das, was es ist: eine Tugend.
Auch die immer ernsteren Zensurbemühungen sind letztlich nur ein Zeichen der Schwäche, wo Argumente fehlen. Sie werden nicht verhindern, dass wir unsere Meinung äußern, unbequeme Fragen stellen und dass die Wahrheit peu à peu ans Licht kommt. Es gibt immer Mittel und Wege, auch für uns.
Danke, dass du diesen Weg mit mir weitergehst!
-
 @ c4551bf3:f041d130
2025-02-10 08:19:46
@ c4551bf3:f041d130
2025-02-10 08:19:466623 là một nền tảng kỹ thuật số tiên tiến, mang đến trải nghiệm trực tuyến mượt mà và ổn định cho người dùng. Với giao diện thân thiện và thiết kế tối ưu, 6623 giúp người dùng dễ dàng truy cập trên cả máy tính và thiết bị di động. Hệ thống được phát triển với công nghệ hiện đại, đảm bảo tốc độ xử lý nhanh, kết nối ổn định và hiệu suất tối ưu, giúp người dùng tận hưởng dịch vụ tiện lợi và liền mạch mọi lúc, mọi nơi.
Một trong những ưu điểm nổi bật của 6623 là sự đổi mới và cập nhật liên tục nhằm nâng cao chất lượng dịch vụ. Nền tảng này luôn tích hợp các công nghệ tiên tiến nhất để tối ưu hóa hiệu suất và mang đến trải nghiệm linh hoạt cho người dùng. Nhờ vào sự cải tiến không ngừng, 6623 tạo ra một không gian giải trí phong phú, hấp dẫn và phù hợp với nhu cầu đa dạng, giúp người dùng luôn có những trải nghiệm trọn vẹn và mới mẻ.
Bên cạnh việc tập trung vào công nghệ, 6623 đặc biệt chú trọng đến bảo mật và quyền riêng tư của người dùng. Hệ thống bảo mật đa lớp với các giao thức mã hóa tiên tiến giúp bảo vệ dữ liệu cá nhân một cách an toàn tuyệt đối. Các biện pháp bảo mật nghiêm ngặt đảm bảo môi trường trực tuyến an toàn, giúp người dùng yên tâm khi trải nghiệm nền tảng mà không lo lắng về các rủi ro bảo mật.
Không chỉ tập trung vào công nghệ hiện đại, 6623 còn cung cấp dịch vụ chăm sóc khách hàng chuyên nghiệp. Đội ngũ hỗ trợ luôn sẵn sàng giải đáp thắc mắc và cung cấp sự trợ giúp nhanh chóng, đảm bảo trải nghiệm người dùng luôn thuận tiện và hài lòng nhất. Sự tận tâm trong dịch vụ là một trong những yếu tố quan trọng giúp 6623 xây dựng lòng tin và sự gắn kết với cộng đồng người dùng.
Với những ưu điểm vượt trội, 6623 không ngừng đổi mới và phát triển để mang đến những trải nghiệm tốt nhất. Nền tảng này liên tục cập nhật công nghệ, mở rộng tính năng và tối ưu hóa dịch vụ nhằm duy trì vị thế hàng đầu trong lĩnh vực giải trí kỹ thuật số. Nhờ vào sự kết hợp giữa công nghệ tiên tiến, bảo mật tối đa và dịch vụ chuyên nghiệp, 6623 đã trở thành một trong những lựa chọn hàng đầu cho những ai tìm kiếm một nền tảng trực tuyến hiện đại, tiện lợi và đáng tin cậy.
-
 @ c11cf5f8:4928464d
2025-02-10 00:35:57
@ c11cf5f8:4928464d
2025-02-10 00:35:57Let's hear some of your latest #Bitcoin purchases, feel free to include links to the #shops or #merchants you bought from too. Any good #deal we should know about?
If you missed our last thread, here are some of the items stackers recently spent and #zap #sats on.
originally posted at https://stacker.news/items/880985
-
 @ 9e69e420:d12360c2
2025-01-19 04:48:31
@ 9e69e420:d12360c2
2025-01-19 04:48:31A new report from the National Sports Shooting Foundation (NSSF) shows that civilian firearm possession exceeded 490 million in 2022. The total from 1990 to 2022 is estimated at 491.3 million firearms. In 2022, over ten million firearms were domestically produced, leading to a total of 16,045,911 firearms available in the U.S. market.
Of these, 9,873,136 were handguns, 4,195,192 were rifles, and 1,977,583 were shotguns. Handgun availability aligns with the concealed carry and self-defense market, as all states allow concealed carry, with 29 having constitutional carry laws.
-
 @ 0fa80bd3:ea7325de
2025-01-29 14:44:48
@ 0fa80bd3:ea7325de
2025-01-29 14:44:48![[yedinaya-rossiya-bear.png]]
1️⃣ Be where the bear roams. Stay in its territory, where it hunts for food. No point setting a trap in your backyard if the bear’s chilling in the forest.
2️⃣ Set a well-hidden trap. Bury it, disguise it, and place the bait right in the center. Bears are omnivores—just like secret police KGB agents. And what’s the tastiest bait for them? Money.
3️⃣ Wait for the bear to take the bait. When it reaches in, the trap will snap shut around its paw. It’ll be alive, but stuck. No escape.
Now, what you do with a trapped bear is another question... 😏
-
 @ 472f440f:5669301e
2024-10-11 14:20:54
@ 472f440f:5669301e
2024-10-11 14:20:54As we sprint toward the 2024 US Presidential election the case for using bitcoin as an asset to store value for the long term has never been stronger. The insanity of the incumbent power structure is being laid bare and it is becoming impossible to ignore the headwinds that the Borg faces moving forward.
Yesterday morning and earlier today it became clear that inflation is rearing its head again. Not ideal for the soft landing Jerome Powell and Yellen are signaling to the markets after the first Fed Funds rate cut in years.
It seems like the yield curve predicted this earlier this week when it inverted after a temporary normalizing period after the Fed's rate cut. Futhermore, it is becoming glaringly obvious that running historically high fiscal deficits while interest rates were at multi-decade highs was a pretty bad idea. As James Lavish points out, the data from the CBO earlier this week shows that the US federal government is running a deficit that is 13% higher than it was last year. This is at a time when real wages are still depressed, inflation is still suffocating American consumers and the private sector job market for American citizens is cratering.
Speaking of the job market, the numbers that came in yesterday were worse than expected: The effect of Hurricane Helene should certainly be taken into consideration when looking at this jobs miss. However, even with the miss we know that these numbers have been under reported for years to make the economy seem healthier than it actually is. Even with Helene's effect taken into consideration this print will likely be revised higher 3-6 months from now.
All of this points to a breaking point. A breaking point for the economy and, more importantly, a breaking point for overall confidence in the US government and its ability to operate with any semblance of fiscal responsibility. The chart that Pierre Rochard shares in the tweet at the top of this letter is the only chart that matters for anyone attempting to gauge where we find ourselves on the path to bitcoin realizing its full potential.
There is $133 TRILLION worth of value sitting in global bond markets. Bitcoin is a far superior asset to store one's wealth in. Bond markets are beholden to the whims of the actors who issue those bonds. In the case of the US Treasury market, the largest bond market in the world, the US government. And as we have pointed out above, the US government is recklessly irresponsible when it comes to issuing debt with a complete inability to pay it back on the long-term. Inflation is up, the jobs market is cratering for the native born Americans who actually pay taxes, and the push toward a multi-polar geopolitical landscape is becoming more pronounced by the day. All of this points to a long-term weakening in demand for US treasuries.
The only way out of this mess is to overtly default on this debt or inflate it away. The latter will most certainly be the route that is taken, which positions bitcoin extremely well as people seek the confines of an asset that cannot be debased because it cannot be controlled by a central authority. The levels of sovereign debt in the world are staggering. Do not let the bitcoin price consolidation of the last six months lull you into a state of complacency. Even the results of the Presidential election won't have a material effect on these dynamics. Though, a Donald Trump presidency would certainly be preferable if you prefer to see relatively sane policy enacted that would provide you with time to find safety in bitcoin. But, in regards to this sovereign debt crisis, that is the only benefit you can hope for; more time to prepare. I'll leave you with some thoughts from Porter Stansberry:
"We are about to see the final destruction of the American experiment. Every economist knows this (see below) is correct; but nobody is going to tell you about it. I’ll summarize in plan English: We are fucked.
-
Debt is growing much faster than GD and interest expense is growing much faster than debt; and the real growth in entitlement spending hasn’t even begun yet.
-
Progressive taxation means nobody will ever vote for less spending + the combined size of government employees and dependents, there’s no way for America’s actual taxpayers (about 20m people) to ever win an election, so the spending won’t stop growing and, ironically, inflation will make demands for more spending to grow.
-
Inflation undermines both economic growth and social cohesion. The purple hair man-women weirdos are only the beginning; what comes next is scapegoating jews, blacks, immigrants and a huge increase in violence/domestic terror.
Get ready America. This election has nothing to do with what’s coming. And neither Trump nor Kamala can stop it.
Our experiment in freedom and self-government died in 1971 (when all restraint on government spending was abandoned with the gold standard.) You can only live at the expense of your neighbor until he runs out of money.
And that day is here."
Final thought... I hope my tux still fits for this wedding. Enjoy your weekend, freaks.Use the code "TFTC" for 15% off
-
-
 @ f7d424b5:618c51e8
2025-02-09 18:33:48
@ f7d424b5:618c51e8
2025-02-09 18:33:48(Copied from my show notes [website](https://melonmancy.net/mp-100-nuance-enjoyer) for Melonmancy)
Promise this isn't normal. It would be disingenuous to not bring it up.
We mentioned a few things in the show you might want to pull up while listening, they are the following:
- Nightmare Kart dev crashes out
- Dr Disrespect gives post-mortem on Midnight Society
- Lords of the Fallen announcement post
Obligatory:
- Listen to the new episode here!
- Discuss this episode on OUR NEW FORUM
- Get the RSS and Subscribe (this is a new feed URL, but the old one redirects here too!)
- Get a modern podcast app to use that RSS feed on at newpodcastapps.com
- Or listen to the show on the forum using the embedded Podverse player!
- Send your complaints here
Reminder that this is a Value4Value podcast so any support you can give us via a modern podcasting app is greatly appreciated and we will never bow to corporate sponsors!
Our podcast is created entirely with free software and is proudly hosted on RSSBlue!
-
 @ ec42c765:328c0600
2025-02-05 23:38:12
@ ec42c765:328c0600
2025-02-05 23:38:12カスタム絵文字とは
任意のオリジナル画像を絵文字のように文中に挿入できる機能です。
また、リアクション(Twitterの いいね のような機能)にもカスタム絵文字を使えます。

カスタム絵文字の対応状況(2025/02/06)

カスタム絵文字を使うためにはカスタム絵文字に対応したクライアントを使う必要があります。
※表は一例です。クライアントは他にもたくさんあります。
使っているクライアントが対応していない場合は、クライアントを変更する、対応するまで待つ、開発者に要望を送る(または自分で実装する)などしましょう。
対応クライアント
ここではnostterを使って説明していきます。
準備
カスタム絵文字を使うための準備です。
- Nostrエクステンション(NIP-07)を導入する
- 使いたいカスタム絵文字をリストに登録する
Nostrエクステンション(NIP-07)を導入する
Nostrエクステンションは使いたいカスタム絵文字を登録する時に必要になります。
また、環境(パソコン、iPhone、androidなど)によって導入方法が違います。
Nostrエクステンションを導入する端末は、実際にNostrを閲覧する端末と違っても構いません(リスト登録はPC、Nostr閲覧はiPhoneなど)。
Nostrエクステンション(NIP-07)の導入方法は以下のページを参照してください。
ログイン拡張機能 (NIP-07)を使ってみよう | Welcome to Nostr! ~ Nostrをはじめよう! ~
少し面倒ですが、これを導入しておくとNostr上の様々な場面で役立つのでより快適になります。
使いたいカスタム絵文字をリストに登録する
以下のサイトで行います。
右上のGet startedからNostrエクステンションでログインしてください。
例として以下のカスタム絵文字を導入してみます。
実際より絵文字が少なく表示されることがありますが、古い状態のデータを取得してしまっているためです。その場合はブラウザの更新ボタンを押してください。

- 右側のOptionsからBookmarkを選択

これでカスタム絵文字を使用するためのリストに登録できます。
カスタム絵文字を使用する
例としてブラウザから使えるクライアント nostter から使用してみます。
nostterにNostrエクステンションでログイン、もしくは秘密鍵を入れてログインしてください。
文章中に使用
- 投稿ボタンを押して投稿ウィンドウを表示
- 顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択
- : 記号に挟まれたアルファベットのショートコードとして挿入される

この状態で投稿するとカスタム絵文字として表示されます。
カスタム絵文字対応クライアントを使っている他ユーザーにもカスタム絵文字として表示されます。
対応していないクライアントの場合、ショートコードのまま表示されます。

ショートコードを直接入力することでカスタム絵文字の候補が表示されるのでそこから選択することもできます。

リアクションに使用
- 任意の投稿の顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択

カスタム絵文字リアクションを送ることができます。

カスタム絵文字を探す
先述したemojitoからカスタム絵文字を探せます。
例えば任意のユーザーのページ emojito ロクヨウ から探したり、 emojito Browse all からnostr全体で最近作成、更新された絵文字を見たりできます。
また、以下のリンクは日本語圏ユーザーが作ったカスタム絵文字を集めたリストです(2025/02/06)
※漏れがあるかもしれません
各絵文字セットにあるOpen in emojitoのリンクからemojitoに飛び、使用リストに追加できます。
以上です。
次:Nostrのカスタム絵文字の作り方
Yakihonneリンク Nostrのカスタム絵文字の作り方
Nostrリンク nostr:naddr1qqxnzdesxuunzv358ycrgveeqgswcsk8v4qck0deepdtluag3a9rh0jh2d0wh0w9g53qg8a9x2xqvqqrqsqqqa28r5psx3
仕様
-
 @ 0fa80bd3:ea7325de
2025-01-29 05:55:02
@ 0fa80bd3:ea7325de
2025-01-29 05:55:02The land that belongs to the indigenous peoples of Russia has been seized by a gang of killers who have unleashed a war of extermination. They wipe out anyone who refuses to conform to their rules. Those who disagree and stay behind are tortured and killed in prisons and labor camps. Those who flee lose their homeland, dissolve into foreign cultures, and fade away. And those who stand up to protect their people are attacked by the misled and deceived. The deceived die for the unchecked greed of a single dictator—thousands from both sides, people who just wanted to live, raise their kids, and build a future.
Now, they are forced to make an impossible choice: abandon their homeland or die. Some perish on the battlefield, others lose themselves in exile, stripped of their identity, scattered in a world that isn’t theirs.
There’s been endless debate about how to fix this, how to clear the field of the weeds that choke out every new sprout, every attempt at change. But the real problem? We can’t play by their rules. We can’t speak their language or use their weapons. We stand for humanity, and no matter how righteous our cause, we will not multiply suffering. Victory doesn’t come from matching the enemy—it comes from staying ahead, from using tools they haven’t mastered yet. That’s how wars are won.
Our only resource is the will of the people to rewrite the order of things. Historian Timothy Snyder once said that a nation cannot exist without a city. A city is where the most active part of a nation thrives. But the cities are occupied. The streets are watched. Gatherings are impossible. They control the money. They control the mail. They control the media. And any dissent is crushed before it can take root.
So I started asking myself: How do we stop this fragmentation? How do we create a space where people can rebuild their connections when they’re ready? How do we build a self-sustaining network, where everyone contributes and benefits proportionally, while keeping their freedom to leave intact? And more importantly—how do we make it spread, even in occupied territory?
In 2009, something historic happened: the internet got its own money. Thanks to Satoshi Nakamoto, the world took a massive leap forward. Bitcoin and decentralized ledgers shattered the idea that money must be controlled by the state. Now, to move or store value, all you need is an address and a key. A tiny string of text, easy to carry, impossible to seize.
That was the year money broke free. The state lost its grip. Its biggest weapon—physical currency—became irrelevant. Money became purely digital.
The internet was already a sanctuary for information, a place where people could connect and organize. But with Bitcoin, it evolved. Now, value itself could flow freely, beyond the reach of authorities.
Think about it: when seedlings are grown in controlled environments before being planted outside, they get stronger, survive longer, and bear fruit faster. That’s how we handle crops in harsh climates—nurture them until they’re ready for the wild.
Now, picture the internet as that controlled environment for ideas. Bitcoin? It’s the fertile soil that lets them grow. A testing ground for new models of interaction, where concepts can take root before they move into the real world. If nation-states are a battlefield, locked in a brutal war for territory, the internet is boundless. It can absorb any number of ideas, any number of people, and it doesn’t run out of space.
But for this ecosystem to thrive, people need safe ways to communicate, to share ideas, to build something real—without surveillance, without censorship, without the constant fear of being erased.
This is where Nostr comes in.
Nostr—"Notes and Other Stuff Transmitted by Relays"—is more than just a messaging protocol. It’s a new kind of city. One that no dictator can seize, no corporation can own, no government can shut down.
It’s built on decentralization, encryption, and individual control. Messages don’t pass through central servers—they are relayed through independent nodes, and users choose which ones to trust. There’s no master switch to shut it all down. Every person owns their identity, their data, their connections. And no one—no state, no tech giant, no algorithm—can silence them.
In a world where cities fall and governments fail, Nostr is a city that cannot be occupied. A place for ideas, for networks, for freedom. A city that grows stronger the more people build within it.
-
 @ e31e84c4:77bbabc0
2024-12-02 10:44:07
@ e31e84c4:77bbabc0
2024-12-02 10:44:07Bitcoin and Fixed Income was Written By Wyatt O’Rourke. If you enjoyed this article then support his writing, directly, by donating to his lightning wallet: ultrahusky3@primal.net
Fiduciary duty is the obligation to act in the client’s best interests at all times, prioritizing their needs above the advisor’s own, ensuring honesty, transparency, and avoiding conflicts of interest in all recommendations and actions.
This is something all advisors in the BFAN take very seriously; after all, we are legally required to do so. For the average advisor this is a fairly easy box to check. All you essentially have to do is have someone take a 5-minute risk assessment, fill out an investment policy statement, and then throw them in the proverbial 60/40 portfolio. You have thousands of investment options to choose from and you can reasonably explain how your client is theoretically insulated from any move in the \~markets\~. From the traditional financial advisor perspective, you could justify nearly anything by putting a client into this type of portfolio. All your bases were pretty much covered from return profile, regulatory, compliance, investment options, etc. It was just too easy. It became the household standard and now a meme.
As almost every real bitcoiner knows, the 60/40 portfolio is moving into psyop territory, and many financial advisors get clowned on for defending this relic on bitcoin twitter. I’m going to specifically poke fun at the ‘40’ part of this portfolio.
The ‘40’ represents fixed income, defined as…
An investment type that provides regular, set interest payments, such as bonds or treasury securities, and returns the principal at maturity. It’s generally considered a lower-risk asset class, used to generate stable income and preserve capital.
Historically, this part of the portfolio was meant to weather the volatility in the equity markets and represent the “safe” investments. Typically, some sort of bond.
First and foremost, the fixed income section is most commonly constructed with U.S. Debt. There are a couple main reasons for this. Most financial professionals believe the same fairy tale that U.S. Debt is “risk free” (lol). U.S. debt is also one of the largest and most liquid assets in the market which comes with a lot of benefits.
There are many brilliant bitcoiners in finance and economics that have sounded the alarm on the U.S. debt ticking time bomb. I highly recommend readers explore the work of Greg Foss, Lawrence Lepard, Lyn Alden, and Saifedean Ammous. My very high-level recap of their analysis:
-
A bond is a contract in which Party A (the borrower) agrees to repay Party B (the lender) their principal plus interest over time.
-
The U.S. government issues bonds (Treasury securities) to finance its operations after tax revenues have been exhausted.
-
These are traditionally viewed as “risk-free” due to the government’s historical reliability in repaying its debts and the strength of the U.S. economy
-
U.S. bonds are seen as safe because the government has control over the dollar (world reserve asset) and, until recently (20 some odd years), enjoyed broad confidence that it would always honor its debts.
-
This perception has contributed to high global demand for U.S. debt but, that is quickly deteriorating.
-
The current debt situation raises concerns about sustainability.
-
The U.S. has substantial obligations, and without sufficient productivity growth, increasing debt may lead to a cycle where borrowing to cover interest leads to more debt.
-
This could result in more reliance on money creation (printing), which can drive inflation and further debt burdens.
In the words of Lyn Alden “Nothing stops this train”
Those obligations are what makes up the 40% of most the fixed income in your portfolio. So essentially you are giving money to one of the worst capital allocators in the world (U.S. Gov’t) and getting paid back with printed money.
As someone who takes their fiduciary responsibility seriously and understands the debt situation we just reviewed, I think it’s borderline negligent to put someone into a classic 60% (equities) / 40% (fixed income) portfolio without serious scrutiny of the client’s financial situation and options available to them. I certainly have my qualms with equities at times, but overall, they are more palatable than the fixed income portion of the portfolio. I don’t like it either, but the money is broken and the unit of account for nearly every equity or fixed income instrument (USD) is fraudulent. It’s a paper mache fade that is quite literally propped up by the money printer.
To briefly be as most charitable as I can – It wasn’t always this way. The U.S. Dollar used to be sound money, we used to have government surplus instead of mathematically certain deficits, The U.S. Federal Government didn’t used to have a money printing addiction, and pre-bitcoin the 60/40 portfolio used to be a quality portfolio management strategy. Those times are gone.
Now the fun part. How does bitcoin fix this?
Bitcoin fixes this indirectly. Understanding investment criteria changes via risk tolerance, age, goals, etc. A client may still have a need for “fixed income” in the most literal definition – Low risk yield. Now you may be thinking that yield is a bad word in bitcoin land, you’re not wrong, so stay with me. Perpetual motion machine crypto yield is fake and largely where many crypto scams originate. However, that doesn’t mean yield in the classic finance sense does not exist in bitcoin, it very literally does. Fortunately for us bitcoiners there are many other smart, driven, and enterprising bitcoiners that understand this problem and are doing something to address it. These individuals are pioneering new possibilities in bitcoin and finance, specifically when it comes to fixed income.
Here are some new developments –
Private Credit Funds – The Build Asset Management Secured Income Fund I is a private credit fund created by Build Asset Management. This fund primarily invests in bitcoin-backed, collateralized business loans originated by Unchained, with a secured structure involving a multi-signature, over-collateralized setup for risk management. Unchained originates loans and sells them to Build, which pools them into the fund, enabling investors to share in the interest income.
Dynamics
- Loan Terms: Unchained issues loans at interest rates around 14%, secured with a 2/3 multi-signature vault backed by a 40% loan-to-value (LTV) ratio.
- Fund Mechanics: Build buys these loans from Unchained, thus providing liquidity to Unchained for further loan originations, while Build manages interest payments to investors in the fund.
Pros
- The fund offers a unique way to earn income via bitcoin-collateralized debt, with protection against rehypothecation and strong security measures, making it attractive for investors seeking exposure to fixed income with bitcoin.
Cons
- The fund is only available to accredited investors, which is a regulatory standard for private credit funds like this.
Corporate Bonds – MicroStrategy Inc. (MSTR), a business intelligence company, has leveraged its corporate structure to issue bonds specifically to acquire bitcoin as a reserve asset. This approach allows investors to indirectly gain exposure to bitcoin’s potential upside while receiving interest payments on their bond investments. Some other publicly traded companies have also adopted this strategy, but for the sake of this article we will focus on MSTR as they are the biggest and most vocal issuer.
Dynamics
-
Issuance: MicroStrategy has issued senior secured notes in multiple offerings, with terms allowing the company to use the proceeds to purchase bitcoin.
-
Interest Rates: The bonds typically carry high-yield interest rates, averaging around 6-8% APR, depending on the specific issuance and market conditions at the time of issuance.
-
Maturity: The bonds have varying maturities, with most structured for multi-year terms, offering investors medium-term exposure to bitcoin’s value trajectory through MicroStrategy’s holdings.
Pros
-
Indirect Bitcoin exposure with income provides a unique opportunity for investors seeking income from bitcoin-backed debt.
-
Bonds issued by MicroStrategy offer relatively high interest rates, appealing for fixed-income investors attracted to the higher risk/reward scenarios.
Cons
-
There are credit risks tied to MicroStrategy’s financial health and bitcoin’s performance. A significant drop in bitcoin prices could strain the company’s ability to service debt, increasing credit risk.
-
Availability: These bonds are primarily accessible to institutional investors and accredited investors, limiting availability for retail investors.
Interest Payable in Bitcoin – River has introduced an innovative product, bitcoin Interest on Cash, allowing clients to earn interest on their U.S. dollar deposits, with the interest paid in bitcoin.
Dynamics
-
Interest Payment: Clients earn an annual interest rate of 3.8% on their cash deposits. The accrued interest is converted to Bitcoin daily and paid out monthly, enabling clients to accumulate Bitcoin over time.
-
Security and Accessibility: Cash deposits are insured up to $250,000 through River’s banking partner, Lead Bank, a member of the FDIC. All Bitcoin holdings are maintained in full reserve custody, ensuring that client assets are not lent or leveraged.
Pros
-
There are no hidden fees or minimum balance requirements, and clients can withdraw their cash at any time.
-
The 3.8% interest rate provides a predictable income stream, akin to traditional fixed-income investments.
Cons
-
While the interest rate is fixed, the value of the Bitcoin received as interest can fluctuate, introducing potential variability in the investment’s overall return.
-
Interest rate payments are on the lower side
Admittedly, this is a very small list, however, these types of investments are growing more numerous and meaningful. The reality is the existing options aren’t numerous enough to service every client that has a need for fixed income exposure. I challenge advisors to explore innovative options for fixed income exposure outside of sovereign debt, as that is most certainly a road to nowhere. It is my wholehearted belief and call to action that we need more options to help clients across the risk and capital allocation spectrum access a sound money standard.
Additional Resources
-
River: The future of saving is here: Earn 3.8% on cash. Paid in Bitcoin.
-
MicroStrategy: MicroStrategy Announces Pricing of Offering of Convertible Senior Notes
Bitcoin and Fixed Income was Written By Wyatt O’Rourke. If you enjoyed this article then support his writing, directly, by donating to his lightning wallet: ultrahusky3@primal.net
-
-
 @ 554ab6fe:c6cbc27e
2025-02-10 16:48:35
@ 554ab6fe:c6cbc27e
2025-02-10 16:48:35René Descartes famously stated, "I think therefore I am." A concept centered around the idea that the existence of our meta-conscious thought proves our existence. Furthermore, it denotes a sense of self-derived from the presence of our thinking. What if this famous idea is wrongly reversed? What if our perceived sense of self derives from our thoughts, and these thoughts act as an illusion of the true nature of the self?
A couple of my posts have focused on the idea that the calm mind, potentially derived from a practice of meditation, can achieve a heightened sense of awareness. Some neuroscientists now view the mind as a predictive modeling machine (Seth, 2013), constantly receiving signals from both internal and external sources, generating predictions and models to understand the current condition. This theory inspired me to create an analogy of a calm pond: Imagine the brain and mind as a pond, and instead of neuronal signals, raindrops are falling into the pond. When the pond is calm, and a single drop falls, the pond's ripples provide adequate information to deduce the location and size of the raindrop. By observing the single ripple, one can simply understand the raindrop. However, if there is a storm and many raindrops impact the pond simultaneously, then the ripples are indistinguishable. This makes the analysis of the incoming information near impossible. This may be how the brain works. This would be why calming the mind generates such benefits in health because the brain can analyze the information accurately and execute the proper response. This idea is supported by scientific evidence that interoception increases with mindfulness practice. I have alluded to this idea as a possible explanation of why meditation generates a higher form of consciousness. More on this later.
To further explore this idea, a deeper exploration into the neuroscience of internal mental processes is required. The areas of the brain that are clinically recognized to perform internal mental operations are known as the default mode network (DMN) (Ekhtiari et al., 2016; van Buuren et al., 2010). The DMN is not a single area of the brain but a network and interaction between many areas. The brain areas involved within the DMN include the medial prefrontal cortex (mPFC), the anterior and posterior cingulate cortex (ACC and PCC), temporoparietal junction (TPJ), later temporal cortex (LTC), and the temporal pole (TempP)(Farb et al., 2007; Zhou et al., 2020). In general, the mental processes conducted by the DMN are self-referential processing, long-term memory retrieval, and mind-wandering (Ekhtiari et al., 2016; Marstaller et al., 2017; Spreng & Grady, 2010; van Buuren et al., 2010). However, the functions expand beyond just those. Different brain areas carry differing roles in these processes. For example, the PCC plays a unique role in the autobiographical retrieval process and plays a role in self-centered spatial navigation (Hamilton et al., 2015). However, sometimes these processes manifest in more complex interactions. For example, both the PCC and anterior portion of the mPFC (amPFC) facilitate self-referential processes and the interaction between other hubs of the DMN (Zhou et al., 2020). The role of the DMN is complicated, but its relationship to meditation is significant.
The DMN's plays a significant role in mental ruminations and the activity of the mind. In our modern culture, mental ruminations are commonplace and widely accepted. With this cultural norm, there is no adequate training to properly handle these thoughts when they become repetitive, unconstructive, and potentially destructive. Repetitive unconstructive ruminations are associated with and can lead to depression (Watkins, 2008). Therefore, this mental habit attributes to a significant source of many mental health issues. It is a primary reason why meditation seems to be such an effective mental health benefiting practice. In Eastern traditions, this unhealthy mind is called the "monkey mind": a mind that swings from thought to thought, often time traveling to the past and future. Meditation, and similar practices, aim to quiet this monkey mind. From a clinical perspective, it is fascinating to consider that the DMN may be a neural network representing the monkey mind's activation. There is research to support this idea as well. Autobiographical memory retrieval processes activate the DMN (Spreng & Grady, 2010). Additionally, the DMN seems to maintain a cohesive perception of the self across time to interpret novel information (Marstaller et al., 2017). Clearly, not only is the DMN involved in processes that involve thoughts about the self, but it is also primarily responsible for our mental time traveling processes. If meditation aims to bring our experience to the present, then the DMN is the antithesis.
As previously stated, mental ruminations and other unconstructive thought patterns drive the development of mental health issues such as anxiety and depression. Given that the DMN has a strong relationship to these thought patterns, it is also interesting to note that DMN activity dominance is associated with the development of depression (Hamilton et al., 2011). The brain areas that seem to be activated more often during depression are the anterior and dorsal regions of the mPFC, PCC, temporal lobes, and the TPJ (Zhou et al., 2020)—further suggesting that the DMN is the brain region highly responsible for our inner self-referential thoughts, our time traveling thoughts, and the subsequent mental health outcomes.
The DMN represents, in large part, the mental activity of the mind that removes us from a calm and present state of being. In other words, it adds more “raindrops” to the calm pond (my analogy from before) making it harder for the brain to analyze and adequately react to incoming information. Evidence for this idea lies in the observation that the DMN is responsible for monkey mind-like processes and in learning and conditioning. Again, the brain is constantly receiving neuronal signals from the body. Say it receives a signal from the toe: it must first predict that the signal came from the toe, then understand what the signal meant, and react accordingly. So, if the signal was a pain signal, the brain may command the toe to lift from the ground. If the signal stops, the brain knows the toe is no longer in pain, verifying the prediction. If the signal doesn't stop, further trial and error are required. This is a simple example, but the brain is likely processing and reacting to signals like this all the time, both from information coming from outside the body and within. Therefore, much learning and prediction model generation is taking place. Imagine the famous experiment of Pavlov's dogs. The dogs learned that a particular cue meant food, and their bodies learned to react accordingly. This learning and conditioning are a fundamental aspect of biological life. The DMN plays a significant role in this learning within our brain. For example, the PCC responds to error detection, and the signal is amplified when small rewards or novel stimuli are introduced to the experience (Heilbronner & Platt, 2013). Areas of the DMN (such as the mPFC and PCC) are also thought to be involved in contextualizing memories of safety and inhibit fear responses when appropriate (Marstaller et al., 2017). Finally, the mPFC is thought to play a role in goal-directed motivation (Hamilton et al., 2015). All this evidence suggests that the DMN plays a significant role in the learning process by contextualizing information.
Keep in mind that the DMN can only accurately contextualize incoming stimuli if the full range of signals is adequately recognized. According to the calm pond idea, the noisy activation of a ruminating mind may hinder this ability. Here, greater clarification and definition on what a polluted mind means is needed. To define such mental patterns, functions of specific DMN regions will be explained. Commonly activated regions within the DMN that involve self-referential processes are (Farb et al., 2007; Knyazev, 2013):
- The orbitomedial prefrontal cortex (omPFC) – which contextualizes experienced stimuli as experienced by the self
- The ACC – which actively monitors the self-experienced stimuli
- The mPFC – which evaluates the self-experienced stimuli
- The PCC – which is involved in a generated a broader context of the personal experience given certain self-experienced stimuli.
By now, it may be evident that the DMN is involved with what is commonly referred to as the "ego". Some researchers claim that the DMN develops the ego itself (R. L. Carhart-Harris & Friston, 2010). The term "ego" derives from Freudian psychoanalytic, and for this reason, the term "narrative-self" will be used instead. It is crucial to consider the word choice here. As previously explained, the DMN generates a time-oriented perception of the self to contextualize information. Furthermore, the four brain areas above all involved contextualizing an experience as experienced by the narrative self (rather than the self being the experience), monitoring these experiences across time, and evaluating these experiences as a broader implication of the experience of the self. The DMN is generating a narrative of the self through every experience. This is indeed where many unconstructive ruminations arise. Any reader can likely relate to ruminating over themselves and their circumstances and thinking about what this means in the larger context of their lives, worth, purpose, etc. This is the monkey mind. This is the DMN.
So, the real question becomes: what effect does the strong presence of a narrative-self have on our broader experience and health? Does a strong presence of the narrative-self influence the body's interoceptive abilities and ability to properly analyze and predict incoming stimuli? This is a complex and challenging question, but evidence suggests that this is indeed the case. In a fantastic study by Farb and others in 2007, fMRIs were used to monitor brain activity in those who did and did not practice mindfulness meditation (Farb et al., 2007). In this study, a distinction was made between narrative focus and experiential focus. For eight weeks, those who underwent mindfulness meditation training were taught to practice experiential focus, which involves having present centered awareness of all thoughts, feelings, and experiences in a non-judgmental manner. Narrative focus was defined as judging experiences and trying to figure out what those stimuli meant. Brain scans were performed on both trained and untrained participants during both focus styles. For both groups, narrative focus increased activation of the mPFC and PCC as expected. During experiential focus, both groups reduced mPFC activity, but only the meditation trained group increased activation of the insula. This is incredible because the insula is highly involved in interoception and the sensations of internal physical states (Fox et al., 2014; Mehling et al., 2012). This study by Farb and others suggests a functional difference between the narrative-self and an experiential-self and shows how the quieting of the narrative-self increases interoceptive abilities and enhances the brains' ability to analyze incoming stimuli properly. Not to mention, this study shows how this skill can be trained.
So far, we have seen how the DMN is involved in the generation of the narrative-self and how this influences our ability to analyze the signals coming from the body. The next reasonable question is to what extent can this be changed? And what are the implications of such change? As was previously shown in the mentioning of the study by Farb and others in 2007, mindfulness meditation appears to be capable of changing DMN activity. This is not the only study to suggest this. Another study showed that meditation decreased mPFC activity in DMN regions, such as the TPJ and PCC (Scheibner et al., 2017). It has also been shown that the neurotransmitter GABA reduces DMN activity, and both yoga and meditation have been implicated in the release of GABA (Guglietti et al., 2013; Hu et al., 2013; Streeter et al., 2018). The release of GABA release is also modulated by the vagus nerve, providing evidence of the possible mechanism at which meditation inhibits DMN activity (Hu et al., 2013; Keute et al., 2018; Streeter et al., 2018). Through these studies, it seems evident that meditation decreases DMN activity. In what ways is this significant? Firstly, it provides more explanation as to why meditation seems capable of alleviating depression. Similarly, it offers more evidence for how meditation increases interoceptive awareness (de Jong et al., 2016; Farb et al., 2010; Hanley et al., 2017). The increase in interoception suggests that the brain is more adequately processing not only the internal environment more adequately, but presumably the outside environment as well. Reality in general is being more accurately understood. It is possible that this also implicates a broader understanding of how meditation can alter consciousness and allowing monks, yogis, and the like to achieve nirvana/samadhi/enlightenment, or whatever you prefer to call such a state of altered consciousnesses. Perhaps this experience of altered consciousness is a more accurate interpretation of reality, produced by enhanced interoception and exteroception.
The subject of altered consciousness is perhaps best explored through brain changes induced by another technique commonly used in a spiritual manner: psychedelics. The famous studies from Johns Hopkins University using psilocybin found that this drug causes a spiritual experience often described as a sense of unity of all things that transcend space and time (Griffiths et al., 2006, 2008). Many participants rate this experience as one of the most significant spiritual experiences of their life (Griffiths et al., 2006). These experiences were often described with an experienced loss sense of self and an altered form of consciousness (Griffiths et al., 2008). It is not hard to imagine that this experience seems very similar to that of a trained monk or yogi, who learn to let go of their narrative-self and gain a sense of oneness with all things. This connection is further verified by the observation that psilocybin decreases the activity of the ACC, PCC, and mPFC (Robin L. Carhart-Harris et al., 2012). Ayahuasca, another psychedelic drug used in spiritual rituals by the indigenous peoples of the Amazon, also has been shown to have similar effects (Palhano-Fontes et al., 2015). Additionally, LSD has been shown to do the same (Speth et al., 2016). Suppose both psychedelic drugs and meditative practice decrease the same DMN, which generates the narrative-self. In that case, both methods likely lead one to the same place: an experience beyond time and space, where one is present with a profound sense of unity with everything.
This, to me, is a profound idea. It suggests that quieting the mind, or calming the “pond”, improves mental, physical, and spiritual health. It provides one with a perception full of compassion, peace, and love. It not only can make the individual healthier, but so too the community and planet. It is extraordinary evidence that improving the self is the greatest means of improving the world around us. Not to mention, it provides a simple means of liberating oneself from the struggle and hardship of life. Perhaps it is not life that is hard on us, but ourselves, by allowing the narrative-mind to take hold of our reality, rather than letting a purer form of consciousness dominate our perceptions. This is the pursuit, and meditation techniques are the practice.
References
Carhart-Harris, R. L., & Friston, K. J. (2010). The default-mode, ego-functions and free-energy: A neurobiological account of Freudian ideas. Brain, 133(4), 1265–1283. https://doi.org/10.1093/brain/awq010
Carhart-Harris, Robin L., Erritzoe, D., Williams, T., Stone, J. M., Reed, L. J., Colasanti, A., Tyacke, R. J., Leech, R., Malizia, A. L., Murphy, K., Hobden, P., Evans, J., Feilding, A., Wise, R. G., & Nutt, D. J. (2012). Neural correlates of the psychedelic state as determined by fMRI studies with psilocybin. Proceedings of the National Academy of Sciences of the United States of America, 109(6), 2138–2143. https://doi.org/10.1073/pnas.1119598109
de Jong, M., Lazar, S. W., Hug, K., Mehling, W. E., Hölzel, B. K., Sack, A. T., Peeters, F., Ashih, H., Mischoulon, D., & Gard, T. (2016). Effects of mindfulness-based cognitive therapy on body awareness in patients with chronic pain and comorbid depression. Frontiers in Psychology, 7(JUN). https://doi.org/10.3389/fpsyg.2016.00967
Ekhtiari, H., Nasseri, P., Yavari, F., Mokri, A., & Monterosso, J. (2016). Neuroscience of drug craving for addiction medicine: From circuits to therapies. In Progress in Brain Research (Vol. 223, pp. 115–141). Elsevier B.V. https://doi.org/10.1016/bs.pbr.2015.10.002
Farb, N. A. S., Anderson, A. K., Mayberg, H., Bean, J., McKeon, D., & Segal, Z. v. (2010). Minding One's Emotions: Mindfulness Training Alters the Neural Expression of Sadness. Emotion, 10(1), 25–33. https://doi.org/10.1037/a0017151
Farb, N. A. S., Segal, Z. v., Mayberg, H., Bean, J., Mckeon, D., Fatima, Z., & Anderson, A. K. (2007). Attending to the present: Mindfulness meditation reveals distinct neural modes of self-reference. Social Cognitive and Affective Neuroscience, 2(4), 313–322. https://doi.org/10.1093/scan/nsm030
Fox, K. C. R., Nijeboer, S., Dixon, M. L., Floman, J. L., Ellamil, M., Rumak, S. P., Sedlmeier, P., & Christoff, K. (2014). Is meditation associated with altered brain structure? A systematic review and meta-analysis of morphometric neuroimaging in meditation practitioners. Neuroscience and Biobehavioral Reviews, 43, 48–73. https://doi.org/10.1016/j.neubiorev.2014.03.016
Griffiths, R. R., Richards, W. A., Johnson, M. W., McCann, U. D., & Jesse, R. (2008). Mystical-type experiences occasioned by psilocybin mediate the attribution of personal meaning and spiritual significance 14 months later. Journal of Psychopharmacology, 22(6), 621–632. https://doi.org/10.1177/0269881108094300
Griffiths, R. R., Richards, W. A., McCann, U., & Jesse, R. (2006). Psilocybin can occasion mystical-type experiences having substantial and sustained personal meaning and spiritual significance. Psychopharmacology, 187(3), 268–283. https://doi.org/10.1007/s00213-006-0457-5
Guglietti, C. L., Daskalakis, Z. J., Radhu, N., Fitzgerald, P. B., & Ritvo, P. (2013). Meditation-related increases in GABAB modulated cortical inhibition. Brain Stimulation, 6(3), 397–402. https://doi.org/10.1016/j.brs.2012.08.005
Hamilton, J. P., Farmer, M., Fogelman, P., & Gotlib, I. H. (2015). Depressive Rumination, the Default-Mode Network, and the Dark Matter of Clinical Neuroscience. In Biological Psychiatry (Vol. 78, Issue 4, pp. 224–230). Elsevier USA. https://doi.org/10.1016/j.biopsych.2015.02.020
Hamilton, J. P., Furman, D. J., Chang, C., Thomason, M. E., Dennis, E., & Gotlib, I. H. (2011). Default-mode and task-positive network activity in major depressive disorder: Implications for adaptive and maladaptive rumination. Biological Psychiatry, 70(4), 327–333. https://doi.org/10.1016/j.biopsych.2011.02.003
Hanley, A. W., Mehling, W. E., & Garland, E. L. (2017). Holding the body in mind: Interoceptive awareness, dispositional mindfulness and psychological well-being. Journal of Psychosomatic Research, 99, 13–20. https://doi.org/10.1016/j.jpsychores.2017.05.014
Heilbronner, S. R., & Platt, M. L. (2013). Causal evidence of performance monitoring by neurons in posterior cingulate cortex during learning. Neuron, 80(6), 1384–1391. https://doi.org/10.1016/j.neuron.2013.09.028
Hu, Y., Chen, X., Gu, H., & Yang, Y. (2013). Resting-state glutamate and GABA concentrations predict task-induced deactivation in the default mode network. Journal of Neuroscience, 33(47), 18566–18573. https://doi.org/10.1523/JNEUROSCI.1973-13.2013
Keute, M., Ruhnau, P., Heinze, H. J., & Zaehle, T. (2018). Behavioral and electrophysiological evidence for GABAergic modulation through transcutaneous vagus nerve stimulation. Clinical Neurophysiology, 129(9), 1789–1795. https://doi.org/10.1016/j.clinph.2018.05.026
Knyazev, G. G. (2013). EEG correlates of self-referential processing. Frontiers in Human Neuroscience, 7(MAY), 1–14. https://doi.org/10.3389/fnhum.2013.00264
Marstaller, L., Burianová, H., & Reutens, D. C. (2017). Adaptive contextualization: A new role for the default mode network in affective learning. Human Brain Mapping, 38(2), 1082–1091. https://doi.org/10.1002/hbm.23442
Mehling, W. E., Price, C., Daubenmier, J. J., Acree, M., Bartmess, E., & Stewart, A. (2012). The Multidimensional Assessment of Interoceptive Awareness (MAIA). PLoS ONE, 7(11). https://doi.org/10.1371/journal.pone.0048230
Palhano-Fontes, F., Andrade, K. C., Tofoli, L. F., Jose, A. C. S., Crippa, A. S., Hallak, J. E. C., Ribeiro, S., & de Araujo, D. B. (2015). The psychedelic state induced by Ayahuasca modulates the activity and connectivity of the Default Mode Network. PLoS ONE, 10(2), 1–13. https://doi.org/10.1371/journal.pone.0118143
Scheibner, H. J., Bogler, C., Gleich, T., Haynes, J. D., & Bermpohl, F. (2017). Internal and external attention and the default mode network. NeuroImage, 148(January), 381–389. https://doi.org/10.1016/j.neuroimage.2017.01.044
Seth, A. K. (2013). Interoceptive inference, emotion, and the embodied self. Trends in Cognitive Sciences, 17(11), 565–573. https://doi.org/10.1016/j.tics.2013.09.007
Speth, J., Speth, C., Kaelen, M., Schloerscheidt, A. M., Feilding, A., Nutt, D. J., & Carhart-Harris, R. L. (2016). Decreased mental time travel to the past correlates with default-mode network disintegration under lysergic acid diethylamide. Journal of Psychopharmacology, 30(4), 344–353. https://doi.org/10.1177/0269881116628430
Spreng, R. N., & Grady, C. L. (2010). Patterns of brain activity supporting autobiographical memory, prospection, and theory of mind, and their relationship to the default mode network. Journal of Cognitive Neuroscience, 22(6), 1112–1123. https://doi.org/10.1162/jocn.2009.21282
Streeter, C., Gerbarg, P. L., Nielsen, G. H., Brown, R. P., Jensen, J. E., Silveri, M., & Streeter, C. C. (2018). Effects of Yoga on Thalamic Gamma-Aminobutyric Acid, Mood and Depression: Analysis of Two Randomized Controlled Trials. Neuropsychiatry, 8(6), 1923–1939. https://doi.org/10.4172/Neuropsychiatry.1000535
van Buuren, M., Gladwin, T. E., Zandbelt, B. B., Kahn, R. S., & Vink, M. (2010). Reduced functional coupling in the default-mode network during self-referential processing. Human Brain Mapping, 31(8), 1117–1127. https://doi.org/10.1002/hbm.20920
Watkins, E. R. (2008). Constructive and unconstructive repetitive thought. Psychological Bulletin, 134(2), 163–206. https://doi.org/10.1037/0033-2909.134.2.163
Zhou, H. X., Chen, X., Shen, Y. Q., Li, L., Chen, N. X., Zhu, Z. C., Castellanos, F. X., & Yan, C. G. (2020). Rumination and the default mode network: Meta-analysis of brain imaging studies and implications for depression. In NeuroImage (Vol. 206, p. 116287). Academic Press Inc. https://doi.org/10.1016/j.neuroimage.2019.116287
-
 @ 9e69e420:d12360c2
2025-01-26 15:26:44
@ 9e69e420:d12360c2
2025-01-26 15:26:44Secretary of State Marco Rubio issued new guidance halting spending on most foreign aid grants for 90 days, including military assistance to Ukraine. This immediate order shocked State Department officials and mandates “stop-work orders” on nearly all existing foreign assistance awards.
While it allows exceptions for military financing to Egypt and Israel, as well as emergency food assistance, it restricts aid to key allies like Ukraine, Jordan, and Taiwan. The guidance raises potential liability risks for the government due to unfulfilled contracts.
A report will be prepared within 85 days to recommend which programs to continue or discontinue.
-
 @ dff95033:862fbf40
2025-02-05 23:19:29
@ dff95033:862fbf40
2025-02-05 23:19:29This event has been deleted; your client is ignoring the delete request.
-
 @ 6ad3e2a3:c90b7740
2025-02-09 11:22:19
@ 6ad3e2a3:c90b7740
2025-02-09 11:22:19I’m honored to have the opportunity to speak with the highly regarded and much beloved Lisbon legend Oscar Liss. Oscar has brought joy to so many children and adults alike. He even helped one person find spiritual salvation, something about which we ask him below. So please enjoy this far-ranging conversation about the meaning life and the nature of consciousness itself.
Q: Oscar, thanks so much for making the time. For the few people that don’t know you, do you mind stating your full name and date of birth?
A: My name is Oscar Liss, though officially it’s Oscar Quinta da Bicherada, the prison complex where I was born. I am a long-haired mini dachshund. I have many aliases, including Osk, Oskie, The Skeeze, Skeezeley, Skeezeley-ski, The Guy, The Guy Behind The Guy, “The Opportunist” (which I don’t like), the…
Q That’s more than sufficient, Oscar, thank you. And date of birth?
A: July 7, 2020.
Q Talk a little bit about your childhood and how you came to live in Lisbon.
A: I was in the prison complex, mostly caged for the first few months. Then I was sold to dog traffickers in Lisbon.
Q: That must have been traumatic.
A: Not really. I quickly developed Stockholm Syndrome. Whenever I see my traffickers now, I feel nothing but overwhelming joy.
Q: Wow. A lot of us can learn from that attitude. Let’s fast forward a bit to your present-day life. In what does it consist?
A: Sleep on the sofa, go for walks, fetch vegetable sticks. Sometimes go for hikes or get sent to dog camp (which is okay, but I’m always the smallest.)
Q: I meant to ask you about your size. I hope it’s not a sensitive subject.
A: I’m six inches tall, more than a foot long, weigh almost 10 pounds.
Q: Are you self-conscious about being a small dog?
A: No, but the traffickers are self-conscious on my behalf. They’re always like, “Who’s the apex predator? Who’s an apex!" Or “you’re such a big strong dog.” It’s absurd. I am fine with who I am.
Q: What’s the source of your self-confidence, I’m sure many of our readers could take a lesson from you.
A: I’m not ambitious. I’m perfectly happy to be a dog.
Q: That’s so profound. Does it not concern you some have described you as “all bark, no bite?”
A: I had a friend once who bit a few people, and they executed him. People mock, but they have no idea the stakes.
Q: Human privilege?
A: Yes. Dogs don’t get due process. There is no justice for a dog.
Q: Do you think there’s species discrimination?
A: Have you ever been rejected from a restaurant and made to wait in the car while everyone else gets in?
Q: How does that make you feel?
A: Bad. I’ve been to many dog-friendly restaurants, never had a problem, aside for that one time I urinated on the coffee shop floor.
Q: Humans often purport to know what a dog is going through, some even create social media accounts for them. What do you think of that?
A: A person of human ancestry can’t possibly know the lived experience of a dog.
Q: You mentioned vegetable sticks. Are you a vegetarian?
A: No. I have never understood the appeal of it. I just like to chew the sticks. (Sometimes I eat apples or bell peppers, but it takes work when you don’t have molars. A lot of “crunch, crunch, crunch” with my jaw.)
Q: What’s behind the alias “The Opportunist” which you said you don’t like.
A: Whenever one of the traffickers opens the refrigerator, I tend to show up in in short order.
Q: I see how that could be insulting. How would you describe your current vocation?
A: I was named “Calorie Acquisition Specialist” recently, but I also work in security.
Q: Security?
A: I make sure to let everyone know when someone’s at the front door.
Q: What goes through your mind in those cases? Are you scared?
A: Not really. Imagine if you were fast asleep and the voice of God at volume 11 screamed into your mind: “WHO THE FUCK IS AT THE DOOR!!!!!!!!!”
Q: Speaking of God, can you tell us about the time you helped a woman on the street connect with Him?
A: We were walking back from Parque Eduardo VII (by the way, Portuguese is my native language), and a woman with two regular size dachshunds, saw me, started shrieking and proclaimed, “your dog is so beautiful he proves the existence of God!”
Q: Wow. It really hit home for her. Let’s talk about your work. How do you stay in character so consistently? How do you maintain your role as a dog?
A: I was incarnated in a dog body and therefore have dog consciousness. Everything I do is a reflection of that basic fact.
Q: Some serious method acting!
A: You could call it that. I am fully immersed in the role.
Q: A lot of humans speak about past lives, can even recall them under hypnosis. Do you think you will be ever reincarnated as a dog, stuck in an infinite dog-loop, so to speak, or will you one day jump into a human body?
A: I don’t know. I focus on the present.
Q: Oscar, it’s been such a pleasure to talk with you. I really appreciate your making the time.
(buzzer sounds)
A: WHO THE FUCK IS AT THE DOOR!!!!!!!!!!!!!!
-
 @ 6bae33c8:607272e8
2025-02-10 15:27:25
@ 6bae33c8:607272e8
2025-02-10 15:27:25I didn’t realize how much I had missed a good old fashioned Super Bowl blowout. I wasn’t even gonna bet the game, but over the last couple days, I got an Eagles vibe. There was too much, “The refs won’t let the Chiefs lose”, and Patrick Mahomes and Taylor Swift, and other noise, and yet the line didn’t budge. It was obvious the Eagles were the sharper side, and they had the league’s best defense, which usually correlates to overperformance of the spread in Super Bowls, sometimes massive overperformance.
But it wasn’t any one thing — just an overall dawning on me that the Eagles were probably the right side. I didn’t feel that strongly about it, even so, and decided I’d just bet Saquon Barkley for MVP, get 3:1 or so if the Eagles won. So I texted someone in the states to place the bet for me, and best he could offer was +175! That’s a terrible value for a RB to win MVP! A few minutes later Tim Schuler offered to bet me $50, give me the Eagles +1, and I obliged him. After that, I texted my friend back to put $500 on the Eagles +1 for me.
Of course, I didn’t stay up all night to watch — after losing 1K on the Falcons (who were up 28-3 in the third quarter at 3 am) eight years ago, never again. So I caught the 40-minute version this morning. What a great game! The Eagles dominated from start to finish. The defensive line got after Mahomes on every play. And while the Chiefs sold out to stop Barkley, Jalen Hurts ran wild on them.
I’m sure I would have enjoyed a Chiefs blowout less, but the beauty of a blowout is it settles things. There’s no looking back at a bad call, a dropped pass or a fumble and wondering what might have been. Close games have drama, but they are more or less arbitrary. I mean I get it, the guy made the throw at the time with the game on the line, but maybe also he just got the cheap roughing the passer call or the ticky tack PI. When the Giants won the Super Bowl on Scott Norwood’s miss, I didn’t have the same sense of satisfaction I did when they blew out John Elway’s Broncos five years earlier. Yes, they won, but it might as well have been on a coin flip.
I grew up on blowouts in the ‘80s — Raiders-Redskins, 49ers-Dolphins, Pats-Bears, Giants-Broncos, Redskins-Broncos — only the Bengals managed to keep Super Bowl losses close (Congratulations Jeff Erickson!) This was before replay reviews and all the lawyering about what is and isn’t a completed catch. The last fucking thing you wanted was some controversy about who really outplayed whom. So it was nice to win some easy money and not to have to worry about refs or fumbles or untimely drops for a change.
-
I wanted Saquon to win MVP, but he drew the attention of the KC defense, is one of the best I’ve ever seen in blitz pickup and still had 97 yards from scrimmage. One of the all-time great years from an all-time great back. (He broke Terrell Davis’ record for the most yardage, regular season and playoffs, too, albeit in two extra games.)
-
Hurts threw the one bad pick under pressure, but it served as a good punt, and otherwise had a near perfect game. Only four other incomplete passes, 72 yards and a score on the ground. He was an easy MVP call.
-
I was a little worried about shaky Jake Elliott, but he drilled all four of his field goals, three of them twice!, due to penalties.
-
Patrick Mahomes padded his stats in garbage time, but he got crushed. An elite defense that gets home with four is the way you kill the GOATS. The Giants did it to Tom Brady twice.
-
Xavier Worthy had a nice garbage-time stat-padding game, but he was the only one. DeAndre Hopkins had a bad drop, though they got him a garbage-time feel-good TD, basically a participation trophy.
-
Congrats to Lane Johnson, Brandon Graham, Elliott and long-snapper Rick Lovato — the only four players in NFL history to defeat both Tom Brady and Mahomes in Super Bowls.
-
The only negative is I lost my $50 four-teams bet with Erickson. I had the Chiefs, Bills, Lions and Ravens, he had the field. But I directed Schuler to pay him, which is good, because I cancelled Paypal for their retarded foray into free-speech policing, and now I don’t have to figure out a workaround.
-
-
 @ 9e69e420:d12360c2
2025-01-25 22:16:54
@ 9e69e420:d12360c2
2025-01-25 22:16:54President Trump plans to withdraw 20,000 U.S. troops from Europe and expects European allies to contribute financially to the remaining military presence. Reported by ANSA, Trump aims to deliver this message to European leaders since taking office. A European diplomat noted, “the costs cannot be borne solely by American taxpayers.”
The Pentagon hasn't commented yet. Trump has previously sought lower troop levels in Europe and had ordered cuts during his first term. The U.S. currently maintains around 65,000 troops in Europe, with total forces reaching 100,000 since the Ukraine invasion. Trump's new approach may shift military focus to the Pacific amid growing concerns about China.
-
 @ 3b7fc823:e194354f
2025-02-09 15:14:10
@ 3b7fc823:e194354f
2025-02-09 15:14:10As someone who takes privacy seriously, I'm always on the lookout for innovative solutions that can help individuals protect their digital lives. One such solution is Tails OS, a Linux-based operating system that's specifically designed for privacy and security.
What is Tails OS?
Tails OS, short for The Amnesic Incognito Live System, is a Debian-based Linux distribution that offers a high level of anonymity and privacy. Developed by the Tails Project, this operating system is designed to preserve your online anonymity and protect your digital identity. Tails OS is a "live" distribution, meaning you can boot it from a USB drive or CD/DVD without installing it on your computer. This makes it an ideal solution for those who need to maintain their privacy while working in public spaces or using public computers.
Why Use Tails OS for Privacy?
Tails OS offers several features that make it an excellent choice for those seeking to protect their online privacy:
- Anonymity: Tails OS uses the Tor network to route your internet traffic through a series of nodes, making it difficult for anyone to trace your online activities back to your physical location.
- Encryption: Tails OS comes with built-in encryption tools, such as GnuPG and OpenSSL, to protect your sensitive data.
- Secure Boot: Tails OS uses a secure boot process to ensure that your system is free from malware and other threats.
- No Persistence: Tails OS is designed to leave no trace on your computer, meaning that any data you create or access while using the operating system will be deleted when you shut down.
Getting Started with Tails OS
Now that you know why Tails OS is an excellent choice for privacy protection, let's dive into the step-by-step guide on how to use it:
Step 1: Download and Create a Tails USB Drive
Visit the Tails website and download the latest version of Tails OS. Follow the instructions to create a bootable USB drive.
Step 2: Boot Tails OS
Insert the USB drive into your computer and restart it. Enter the BIOS settings (usually by pressing F2, F12, or Del) and set the USB drive as the first boot device. Save the changes and exit the BIOS settings. Your computer will now boot from the Tails USB drive.
Step 3: Security implications of setting up an administration password For better security, no administration password is set up by default. When you set up an administration password, an attacker who can get physical access to your computer while Tails is running could be able to break your security
Step 4: Configure Tails OS
Tails OS comes with a pre-configured Tor network, which is enabled by default. You can also configure other settings, such as the keyboard layout and language, from the "Settings" menu.
Step 5: Use Tails OS for Private Activities
Now that you're logged in and configured, you can use Tails OS for private activities, such as:
- Browsing the internet anonymously using Tor
- Sending and receiving encrypted emails using GnuPG
- Creating and editing documents using LibreOffice
- Chatting with friends and family using Pidgin
- Setup Persistent Storage for files
Emergency shutdown To trigger an emergency shutdown, unplug the USB stick from which Tails is running. Doing so might be faster than shutting down from the system menu.
NOTE: You risk breaking your Persistent Storage and losing data when you unplug your USB stick while Tails is running.
Conclusion
Tails OS is an excellent tool for anyone seeking to protect their online privacy. With its built-in anonymity features, encryption tools, and secure boot process, Tails OS provides a high level of protection for your digital identity. By following the step-by-step guide outlined above, you can start using Tails OS for private activities and take control of your digital life.
Remember, privacy is a fundamental human right, and it's essential to take steps to protect it. Tails OS is an excellent tool for anyone looking to maintain their online anonymity and protect their digital identity.
Advocating for privacy does not finance itself. If you enjoyed this article, please consider zapping or sending monero
82XCDNK1Js8TethhpGLFPbVyKe25DxMUePad1rUn9z7V6QdCzxHEE7varvVh1VUidUhHVSA4atNU2BTpSNJLC1BqSvDajw1
-
 @ 3bf0c63f:aefa459d
2024-09-06 12:49:46
@ 3bf0c63f:aefa459d
2024-09-06 12:49:46Nostr: a quick introduction, attempt #2
Nostr doesn't subscribe to any ideals of "free speech" as these belong to the realm of politics and assume a big powerful government that enforces a common ruleupon everybody else.
Nostr instead is much simpler, it simply says that servers are private property and establishes a generalized framework for people to connect to all these servers, creating a true free market in the process. In other words, Nostr is the public road that each market participant can use to build their own store or visit others and use their services.
(Of course a road is never truly public, in normal cases it's ran by the government, in this case it relies upon the previous existence of the internet with all its quirks and chaos plus a hand of government control, but none of that matters for this explanation).
More concretely speaking, Nostr is just a set of definitions of the formats of the data that can be passed between participants and their expected order, i.e. messages between clients (i.e. the program that runs on a user computer) and relays (i.e. the program that runs on a publicly accessible computer, a "server", generally with a domain-name associated) over a type of TCP connection (WebSocket) with cryptographic signatures. This is what is called a "protocol" in this context, and upon that simple base multiple kinds of sub-protocols can be added, like a protocol for "public-square style microblogging", "semi-closed group chat" or, I don't know, "recipe sharing and feedback".
-
 @ da0b9bc3:4e30a4a9
2025-02-10 12:51:46
@ da0b9bc3:4e30a4a9
2025-02-10 12:51:46Hello Stackers!
It's Monday so we're back doing "Meta Music Mondays" 😉.
From before the territory existed there was just one post a week in a ~meta take over. Now each month we have a different theme and bring music from that theme.
Welcome to Femmes Fatales 3!!!
I absolutely loved doing this last year so I'm bringing it back for round 3!
It's Femmes Fatales, where we celebrate women in ~Music. So let's have those ladies of the lung, the sirens of sound, our Femmes Fatales!
https://youtu.be/ya69LUa1E_w?si=cM6yCALsPpp9L3Sc
I recently got introduced to these ladies. Their music is fantastic, they're really talented musicians. They are:
Lilith: The vocalist. Lamia: The lead guitarist. Nixe: The bassist. Abrahel: The drummer.
Their identity is meant to be a mystery, so let's keep it that way.
These Nuns can make Noise!!
Let's go!
Talk Music. Share Tracks. Zap Sats.
originally posted at https://stacker.news/items/881416
-
 @ 472f440f:5669301e
2024-09-25 04:12:35
@ 472f440f:5669301e
2024-09-25 04:12:35Last night I had the pleasure of sitting down with Caitlin Long, Founder and CEO of Custodia - a fully reserved bank providing banking services to bitcoin companies, to discuss an affidavit written by Elaine Hetrick of Silvergate Bank. Elaine is the Chief Administrative Officer of Silvergate and wrote an affidavit, a sworn testimony subject to perjury, in which she detailed the events that led to Silvergate voluntarily winding down their business and returning deposits to their customers.
This affidavit is a bombshell because it confirms speculation that Silvergate was solvent in early 2023 and wasn't shut down because of bad risk management on behalf of the bank's management team, but instead was forced to shutter its doors because the Biden Administration, with strong influence from Senator Elizabeth Warren, forced Silvergate's hand because they didn't like that they were banking digital asset companies.
For those who are a bit fuzzy on the details of the narratives that were flying around Silvergate at the time, I'll jog your memory. FTX was a customer of Silvergate's at the time their Ponzi scheme unraveled. As FTX was blowing up, everyone and their mother was scrambling to get their money out of Silvergate because they assumed that since one of the bank's largest counterparties was going bust, the bank must be in trouble too. A sane decision. Especially considering the history of systemically non-important financial institutions this century.
Unless you were paying close attention during this time, you were likely under the impression that Silvergate was a typical fractionally reserved bank that was experiencing a run that led to its inevitable demise. The media made it seem this way. The regulators made it seem this way. And one pompous short seller made it seem this way. However, nothing could be further from the truth. Here are the most important parts of the affidavit:
Silvergate had stabilized, was able to make regulatory capital requirements, and had the capability to continue to serve its customers that had kept their deposits with Silvergate Bank.
Despite this, regulators decided to turn the pressure up and essentially gave Silvergate Bank, and Signature Bank as well, an ultimatum; drastically change your business models immediately by dropping your digital asset customer base or we'll shut you down. There were no hard numbers described in Elaine's testimony, but rumors are that the regulators wanted Silvergate to quickly shrink their exposure to digital asset-related clients to less than 15% of their capital base. At the time, Silvergate's customer base was made up almost entirely of digital asset companies (99.5% to be exact).
The regulators were asking Silvergate to do something that was quite literally impossible given the circumstances. Faced with an impossible task, on March 8th of 2023 Silvergate decided to voluntarily wind down their operations and return deposits back to their customers.
Let's be very clear here, Silvergate did not lose a single penny of customer deposits due to the run on their bank. Management, understanding the volatile nature of the digital asset markets, designed their risk management and capital allocation strategies in a way that would enable them to return dollars to any customer who requested them. And that's exactly what they did when customers came to request their money. They returned EVERY SINGLE PENNY.
This begs the question, "Why did they essentially force Silvergate to shut down?" They seemed to be running a very responsible operation after all. You'd think the regulators would applaud Silvergate's vigilance in risk management on behalf of their customer base. How many banks would have been able to do the same thing if put in the same situation? Probably not many.
The answer to this question is already well known throughout the industry, but Elaine Hetrick's testimony adds some hard evidence that makes it undeniable; Elizabeth Warren, the SEC, the FDIC and the Federal Reserve have been acting in concert to unconstitutionally and extrajudicially target the bitcoin and broader digital asset industry because they do not believe that it should exist. It is a threat to their power structure. The financial system, as it is designed today, gives those who would like to centrally plan the economy and micromanage the lives of American citizens a ton of power. Bitcoin is a threat to that power and they have to do everything in their power to prevent its proliferation.
The targeting of the industry was also confirmed by the aftermath of the NYDFS and FDIC uncharacteristically taking Signature Bank behind the woodshed in the evening of Sunday, March 20th, 2023, despite the fact that Barney Frank and others at the bank were convinced they could handle withdraws come market open the next day.
Signature Bank was ultimately sold to Flagstar Bank. However, they were forced to spin out their digital asset-related accounts before doing so.
This public signaling and sudden regulatory shift made clear that, at least as of the first quarter of 2023, the Federal Bank Regulatory Agencies would not tolerate banks with significant concentrations of digital asset customers, ultimately preventing Silvergate Bank from continuing its digital asset focused business model.
Pretty damning if you ask me. Also, very frustrating and most definitely illegal.
Elizabeth Warren and her gaggle of hall monitors across alphabet soup agencies and the Federal Reserve have been on one massive, unconstitutional, power trip for the last four years. They've besmirched bitcoin and those of us working hard to ensure that the United States of America leads the way forward as bitcoin adoption continues at every turn. Good people striving to make the world a better place.
No one is a better example of this than Alan Lane, the former CEO of Silvergate Bank. I consider Alan a friend and feel supremely confident when I say that he is one of the nicest and thoughtful people I have met in this industry. A man who followed his passion to bring legitimacy and much needed banking services to an industry that the incumbents refused to touch. And he did bring legitimacy. As I explained earlier, Alan and his team understood the volatile nature of the industry and built their firm in a way that took this volatility into account. Silvergate did not fail, they were forced to shut down by Elizabeth Warren and her acolytes at the regulatory agencies.
What's worse, Warren's vendetta against bitcoin and the digital asset industry incited the largest banking crisis this country had seen since 2008. Silvergate and Signature being taken behind the woodshed put everyone on their toes and bank runs started across the country. This led to the failure of First Republic, Silicon Valley Bank and a couple of smaller banks, forced the Fed to step in with their emergency BTFP program, and burdened taxpayers with $40B in FDIC costs that needed to be absorbed as a result. If it weren't for the bailouts things would have gotten completely out of control. All because Elizabeth Warren wants to live in a world in which we are forced to use CBDCs and unable to opt-in to bitcoin.
The euthanasia of Silvergate and Signature are only the tip of the iceberg when it comes to Chokepoint 2.0.
Caitlin Long and Custodia have been in a years long battle with the Federal Reserve to receive a Fed master account so that they can properly serve their customers. For those who are unaware, Custodia is a full-reserve bank that exist to serve bitcoin and digital asset businesses as well as other adjacent businesses like fintechs, banks and funds. Custodia is a chartered bank and special purpose depository institution that has built custody services so that customers can hold bitcoin within their bank accounts alongside their dollar accounts.
Like Silvergate and Signature, Custodia has been singled out and unlawfully denied a master account with the Fed because the Federal Reserve doesn't want a bank like Custodia to exist. Either because they worry about the ramifications of the introduction of a full-reserve bank into a system dominated by fractional-reserve banks or they simply do not want to see bitcoin succeed. If we're being honest, it's probably a combination of the two.
Despite what we, or anyone else, thinks about the potential effect a bank like Custodia could have on the market if it's granted a master account, the Fed's actions are unconstitutional in this case as well. This was made pretty clear (but yet to be determined by a court) in an amicus brief written by Paul Clement on behalf of Custodia earlier this Summer. The Fed is actively undermining the dual-banking system that was set up in this country to enable competition between state chartered banks and the Federal Reserve system.
In the case of Custodia, the Federal Reserve is exhibiting expansive discretionary power that it has never shown before. Custodia is a state chartered special purpose depository institution in the state of Wyoming. Historically, it would be trivial for this type of state chartered bank to get a master account with the Fed. But for whatever reason (we know the reason) the Fed has been denying Custodia their right to this account for a number of years. To the point where Custodia was forced to sue the Federal Reserve and take their case to the courts.
What's interesting about the saga of Custodia and the Fed is that it has forced Custodia's legal team to dig in and highlight where the Fed is overextending its reach and acting arbitrarily. In the amicus brief that was published in July of this year, Paul Clement argues that the way Federal Reserve Bank presidents are chosen is unconstitutional when you take into consideration the fact the these Fed branch presidents are unilaterally undermining state banking laws by denying master accounts.
If they are going to unilaterally undermine state banking laws they need to be appointed by the President or an official acting on behalf of the Executive Branch. Federal Reserve Bank presidents aren't appointed by the President of the United States or any official acting with the authority of the Executive Branch. Instead, they are appointed by their boards, which are controlled by the privately held commercial banks who own them. The Federal Reserve system is clearly acting unconstitutionally when they deny Custodia from being assigned a master account.
The people in power within the federal government and the Federal Reserve system are actively targeting the bitcoin and digital asset industry, acting extrajudicially and making a mockery of the rule of law in the United States. They are completely out of control and it is important that everyone who cares about the future of bitcoin in the United States and the future of the United States more broadly (even if you don't like bitcoin) speaks out and fights against these totalitarians as vehemently as possible. What they are doing is wrong. It's unconstitutional. And it is putting the future of our country at risk.
If the federal government, the regulators and the Federal Reserve do not get out of the way and let law abiding citizens build the businesses they want and associate with businesses they want, those businesses will go elsewhere and the United States will be set back generations as a result.
It's time to put these people in their place and let it be known that freedom will reign supreme in the Land of the Free. Fight!
Final thought... I promised Parker Lewis that I would do cross fit on Friday morning and I'm using today's final thought as an accountability tool.
-
 @ 472f440f:5669301e
2024-09-23 22:33:24
@ 472f440f:5669301e
2024-09-23 22:33:24While most of the world is focused on the lead up to the Presidential election here in the US and louder war drums being beat across the world, the number of bullish developments that are stacking up for bitcoin is increasing rapidly. These developments deserve the OG Marty's Bent smorgasbord treatments, so here are the things that have caught my attention over the last week in no particular order.
The First Ark Transactions on Bitcoin Mainnet
I had the pleasure of participating in a demo of Second's Ark protocol implementation. For those who are unaware, Ark is a new layer-two protocol solution for making off-chain bitcoin payments. Unlike the lightning network, Ark doesn't depend on liquidity channels to facilitate payments. Within the lightning network two counterparties share UTXOs within a channel to move sats back and forth, nodes connect to many different channels to create a network effect that increases the chance of payments getting routed successfully, and node operators manage their channel liquidity as channel imbalances emerge.
Ark is similar in the sense that it also leverages a shared UTXO model. However, instead of having one-to-one channels that come with liquidity management issues, Ark enables a large amount of individuals to share UTXOs, which are managed by an Ark Service Provider (ASP). The ASP is a central party within the protocol, but it is a central party that does not custody UTXOs. It only coordinates the transfer of sats between Ark "rounds". Users have the ability to unilaterally exit the second-layer protocol whenever they deem necessary by broadcasting a Virtual UTXO (vtxo) transaction.
This may seem daunting and complicated. All you need to know is that there is now an new way to make off-chain bitcoin payments that are fast and relatively cheap and it is possible today. As it stands today, Ark has some scaling limitations that can be solved if covenants get merged into the bitcoin protocol, which would significantly reduce the data requirements for signing this type of transaction.
It should also be noted that Ark isn't here to replace the lightning network. It can help serve different use cases and, at the same time, significantly improve the UX of the lightning network. Particularly channel management. The progression of the Ark protocol is a welcomed development. I look forward to following what's going on with Ark as the protocol matures.
The Kingdom of Bhutan is Stacking A LOT of Sats
We were made aware of the fact that the Kingdom of Bhutan, a small country in the Himalayas with a population less than 1,000,000 people, was mining bitcoin in early 2023 when their sovereign wealth fund was doxxed in the bankruptcy proceedings of BlockFi and Celsius. Don't look now, but Bhutan has been doxxed again, this time by the chain surveillance firm Arkham, which is reporting that the nation currently holds more than 13,000 bitcoin, which is nearly 1/3 of its GDP. Driven predominately by its mining operations, which have expanded significantly over the last two years in an attempt to monetize the country's excess hydroelectric power.
While we're not big fans of doxxing here at TFTC, we are fans of the game theory of bitcoin playing out in front of our eyes. And the Kingdom of Bhutan is a shining example of the game theory bitcoiners have been talking about for 15 years playing out perfectly.
Bitcoin is a very thorny topic for individuals at every layer of society. At the individual layer, people have to independently decide that bitcoin is a better money and they have to actively decide to store their wealth in it instead of other assets. For companies, the decision to use bitcoin as the preferred savings vehicle is even harder because most businesses have multiple stakeholders that need to align on a decision before making it. When you move up to the nation state level, the complexity of making the decision to add bitcoin as a strategic reserve asset gets even harder. Many more people and different branches of government need to agree and pass bills (in most cases) before bitcoin can ever make it into a nation's treasury asset mix.
It has long been said within bitcoin circles that individuals who have the ability to think independently, companies that have a lean corporate structure, and nation states with little to lose will be the first movers into bitcoin. And they will benefit massively over the long-run for being early.
If you're an individual reading this who is using bitcoin as their money of choice, you are one of these early movers. Microstrategy under Michael Saylor, who has the ability to make somewhat unilateral decisions due to the company's share structure, is an early move. And, Bhutan, a small nation in the Himalaya mountains with a sovereign wealth fund that seems to have the ability to take risk, is an early mover. With little to lose and greatness to gain, Bhutan is giving other small nation states the playbook for leap frogging the competition in the digital age. Stack a shit ton of bitcoin on the DL, hold on to it for a considerable amount of time, and wake up one day as an economic powerhouse.
The Fed Cuts Rates by 50 Basis Points
I'm sure all of you are well aware at this point. Last week the Federal Reserve made it's first rate cuts in over four years when it cut the fed funds target rate by 0.50% to 4.75-5.00%. With the economy reeling despite what the official government and mainstream narrative may try to make you believe, Jerome Powell and crew have decided it is time to ease up on their monetary policy.
Put another way, inflation is likely to come back with a vengeance as easy money begins to reenter the economy. To be clear, a lower fed funds rate doesn't technically necessitate that newly printed dollars enter the economy like they have over the last 15 years via operations like quantitative easing. However, one has to imagine that the Fed sees some sort of liquidity crisis on the horizon that requires them to begin cutting rates. And not only cutting, but cutting at a pace that was very low probability only a couple of months ago. The consensus in the middle of the Summer was that the Fed would begin lowering rates with a modest 25bps cut this month. They doubled that.
It's probably safe to assume that something is approaching a breaking point on the back end of the financial system. One only has to look at record high credit card debt, record low savings rates, the state of the job market for native born Americans, and the continued turn over of commercial real estate markets to see that not all is well in the American economy. Your Uncle Marty's spidey senses are signaling that a liquidity crunch is likely lurking around the corner. When it does rear its ugly head, you can expect quantitative easing to make a big come back.
When money printer goes brrr, bitcoin goes berserk.
It seems that the Treasury's move over the last 18-months of over-indexing on the front end of the curve during their auctions is already having an expansionary effect on M2 as it has officially entered expansion territory for the first time since 2022. Hold on to your butts, freaks.
Bitcoin's fundamentals are only getting stronger as time goes on. This is evidenced by continued improvement to the protocol stack via second layer protocols, continued adoption by reputable actors like the Kingdom of Bhutan, and the continued mismanagement of the fiat monetary system.
The price of bitcoin has been range bound since the Spring and it has lulled the market into a state of boredom. Enjoy the boring period while it lasts. All signs are pointing to a bitcoin bull run the likes of which the world hasn't seen before. There is a lot of tinder, it is extremely dry, and there are flame throwers on the horizon.
Final thought... Nothing makes me happier than meeting someone who gets value from this newsletter or the podcasts in the wild. Love you, freaks.
-
 @ a012dc82:6458a70d
2025-02-08 22:44:44
@ a012dc82:6458a70d
2025-02-08 22:44:44The world of cryptocurrency has always been a rollercoaster of highs and lows, but recent developments in the Bitcoin market have caught the attention of investors worldwide. The circulating supply of Bitcoin in profit has surged to a multi-year high, a phenomenon not seen since the heady days of November 2021 when Bitcoin reached its all-time high. This significant milestone, backed by data from industry analysts at Glassnode and a detailed report from Bitfinex, paints a picture of a robust Bitcoin market. The implications of this surge are far-reaching, affecting not just seasoned cryptocurrency traders but also new investors who are contemplating dipping their toes into the Bitcoin pool. This article aims to dissect this trend, exploring its roots, its impact on the market, and what it potentially spells out for the future of Bitcoin investment.
Table Of Content
-
Understanding the Surge
-
Implications for Long-term Investors
-
Market Strength and Investor Confidence
-
Potential Early Signs of a Bull Market
-
Caution and Market Dynamics
-
Conclusion
-
FAQs
Understanding the Surge
The surge in Bitcoin's circulating supply in profit is a complex phenomenon, driven by a confluence of market dynamics and investor behavior. The recent increase in Bitcoin's price, which saw it soar above $37,000, is a primary factor. This price hike has pushed a significant portion of Bitcoin into profitable territory. According to the Bitfinex report, over 16.3 million Bitcoin, a staggering amount by any measure, are currently in profit. This figure is considerably higher than the historical average, suggesting a market that is not only recovering but thriving. The surge is not just a momentary blip but a reflection of deeper market trends, including increased institutional interest in Bitcoin, broader acceptance of cryptocurrencies as a legitimate asset class, and the growing perception of Bitcoin as a hedge against inflation and currency devaluation.
Implications for Long-term Investors
For long-term investors, this surge in Bitcoin's profitability is a beacon of stability in the typically volatile cryptocurrency market. The fact that 70% of Bitcoin's total circulating supply has remained static over the past year is indicative of a maturing market where investors are increasingly viewing Bitcoin as a long-term investment rather than a quick profit opportunity. This holding pattern contributes to a tightening of supply, which, coupled with increasing demand, can lead to a sustained price increase. However, long-term investors should also be aware of the potential risks. The cryptocurrency market is still relatively young and can be influenced by regulatory changes, technological advancements, and shifts in investor sentiment. Therefore, while the current trend is encouraging, it should be viewed within the broader context of market dynamics.
Market Strength and Investor Confidence
The current state of the Bitcoin market is a testament to its growing strength and the confidence it instills in investors. With a majority of holders seeing positive returns, there's a renewed vigor in the market, attracting both retail and institutional investors. This influx of new investment can further stabilize the market and potentially drive prices higher. However, this increased investor confidence must be tempered with a degree of caution. The cryptocurrency market is known for its rapid fluctuations, and what goes up can just as quickly come down. Investors should be mindful of the inherent risks and conduct thorough research before making any investment decisions. The market's strength, while promising, is not a guarantee of future performance, and a prudent investment strategy should always be in place.
Potential Early Signs of a Bull Market
The analysis by Bitfinex suggests that the market might be in the early stages of a bull market. This is a significant indicator for investors, as bull markets are characterized by rising prices and increased buying activity. If this trend continues, it could lead to substantial gains for those invested in Bitcoin. However, predicting market movements, especially in the volatile world of cryptocurrencies, is fraught with uncertainty. While the signs are positive, they are not infallible indicators of future performance. Investors should therefore approach this potential bull market with optimism tempered by realism, recognizing that market conditions can change rapidly and without warning.
Caution and Market Dynamics
In the face of these optimistic trends, a word of caution is warranted. The cryptocurrency market is notoriously unpredictable, and while the current indicators are positive, they are not immune to sudden and unexpected changes. Factors such as regulatory announcements, technological breakthroughs, or macroeconomic shifts can rapidly alter the market landscape. Therefore, investors should remain vigilant, keeping abreast of market news and trends. Diversification of investments, a keen understanding of market dynamics, and a clear investment strategy are essential tools in navigating the complexities of the Bitcoin market.
Conclusion
The surge in Bitcoin's circulating supply in profit to a multi-year high marks a significant milestone in the cryptocurrency's journey. It reflects a market that is gaining maturity, strength, and the confidence of its investors. This development could herald the beginning of a new era for Bitcoin, characterized by stability and sustained growth. However, the path of Bitcoin and the broader cryptocurrency market remains unpredictable. Investors should therefore approach this market with a well-informed strategy, balancing optimism with a healthy dose of caution. In the ever-evolving world of cryptocurrency, staying informed and adaptable is key to navigating the market's highs and lows.
FAQs
How does this surge affect long-term investors? Long-term investors may see this as a sign of market stability and maturity, indicating that Bitcoin is increasingly being viewed as a viable long-term investment.
Could this trend indicate the start of a Bitcoin bull market? While the surge in profitable Bitcoin supply could be an early sign of a bull market, predicting market movements in the volatile cryptocurrency sector is complex and uncertain.
What percentage of Bitcoin's circulating supply is currently in profit? Over 83% of Bitcoin's circulating supply is reported to be in profit, according to recent data.
What should investors be cautious about in light of this surge? Investors should be aware of the inherent volatility in the cryptocurrency market and consider factors like regulatory changes, technological advancements, and broader market dynamics before making investment decisions.
How does the current Bitcoin market compare to historical averages? The current percentage of Bitcoin in profit is significantly higher than the historical average, indicating a particularly strong market phase.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 9e69e420:d12360c2
2025-01-21 19:31:48
@ 9e69e420:d12360c2
2025-01-21 19:31:48Oregano oil is a potent natural compound that offers numerous scientifically-supported health benefits.
Active Compounds
The oil's therapeutic properties stem from its key bioactive components: - Carvacrol and thymol (primary active compounds) - Polyphenols and other antioxidant
Antimicrobial Properties
Bacterial Protection The oil demonstrates powerful antibacterial effects, even against antibiotic-resistant strains like MRSA and other harmful bacteria. Studies show it effectively inactivates various pathogenic bacteria without developing resistance.
Antifungal Effects It effectively combats fungal infections, particularly Candida-related conditions like oral thrush, athlete's foot, and nail infections.
Digestive Health Benefits
Oregano oil supports digestive wellness by: - Promoting gastric juice secretion and enzyme production - Helping treat Small Intestinal Bacterial Overgrowth (SIBO) - Managing digestive discomfort, bloating, and IBS symptoms
Anti-inflammatory and Antioxidant Effects
The oil provides significant protective benefits through: - Powerful antioxidant activity that fights free radicals - Reduction of inflammatory markers in the body - Protection against oxidative stress-related conditions
Respiratory Support
It aids respiratory health by: - Loosening mucus and phlegm - Suppressing coughs and throat irritation - Supporting overall respiratory tract function
Additional Benefits
Skin Health - Improves conditions like psoriasis, acne, and eczema - Supports wound healing through antibacterial action - Provides anti-aging benefits through antioxidant properties
Cardiovascular Health Studies show oregano oil may help: - Reduce LDL (bad) cholesterol levels - Support overall heart health
Pain Management The oil demonstrates effectiveness in: - Reducing inflammation-related pain - Managing muscle discomfort - Providing topical pain relief
Safety Note
While oregano oil is generally safe, it's highly concentrated and should be properly diluted before use Consult a healthcare provider before starting supplementation, especially if taking other medications.
-
 @ 472f440f:5669301e
2024-09-18 02:15:29
@ 472f440f:5669301e
2024-09-18 02:15:29As I'm sure many of you are aware already, Israel executed an attack on thousands of Hezbollah members in Lebanon earlier today. At the moment, it looks like Israel successfully waged a supply chain attack on the pagers used by Hezbollah members. Intercepting the devices and placing highly explosive material on the batteries that could be triggered remotely by raising the temperature of the batteries.
To my knowledge, this is the first time an attack of this nature and of this scale has ever been waged. This is a very serious and dangerous precedent that should make anyone reading this think long and hard about the ramifications of the normalization of this type of warfare.
It's not clear to me yet whether this is exactly what happened, but this seems to be where all of the reports are pointing. And when you consider the scale of this operation, it is hard to think of alternative ways that this could have been achieved outside of corrupting the supply chain of this particular pager. Regardless, the die has been cast and remote detonation attacks in crowded civilian areas has been battle tested as an appropriate war tactic.
Not only does this set a terrible precedent for war, but it also begs the question; if they can do something like this with a relatively dumb pager, how much damage could they do with something like an iPhone? How vulnerable are the billions of people who hold smartphones in their pockets, or drive internet connected electric vehicles with lithium ion batteries? How trivial was it for Mossad to gain access to these devices and at what part of the supply chain? Now that this attack has been deemed to be "on the table" how long will it take before others begin to wage similar attacks?
War tactics and their costs are rapidly changing right before our eyes. The war between Russia and Ukraine is showing that low cost drones strapped with bombs can be very effective weapons that can do damage to military equipment worth anywhere between tens of millions to billions of dollars. The Houthi rebels have used cheap drones to completely disrupt the Suez Canal for the better part of a year. The world has only seen the tip of the iceberg in regards to how this type of technology can be used at scale to tip the leverage of power towards those with less financial resources, but a willingness to engage in kinetic conflict. Some of these drones are strapped with thermite flame throwers!
Now that new information has been brought to the market - you can turn pagers and (likely) cellular phones into a network of improvised explosive devices via a software push that increases the temperature of the devices' batteries - it is only a matter of time before others figure out how to do it and begin using these tactics themselves. War machines have never been easier and cheaper to deploy. In a world that is becoming increasingly fractured and angry, this is absolutely frightening. Asymmetric warfare as predicted in the Sovereign Individual is upon us.
As it relates to bitcoin hardware, these attacks highlight that an attack that has been long talked about in the industry but not yet exploited to the best of our knowledge is very real. Supply chain attacks, particularly on bitcoin signing devices that store private key information, have just been proven to be very possible by motivated state actors. If a nation state wanted to somehow "prove" that bitcoin is insecure or figure out a low effort way to do a mass confiscation of bitcoin all they have to do is successfully attack the supply chain of a hardware manufacturer, corrupt the devices, and let them flow to the hands of individuals who believe they are securing their bitcoin in the best way possible. The best way to mitigate this risk is to hold you bitcoin in a multi-sig wallet using a quorum of keys produced by different hardware produced by different manufacturers. Companies like Unchained make this process as seamless and possible and supply chain attacks like the one that was laid bare today highlight why these collaborative custody models are so important. Especially if you are holding a large amount of wealth in bitcoin.
This is a sad day for the world. I'll be praying for peace and sanity to prevail.
Final thought... That was a terrible loss by the Birds.
-
 @ 76c71aae:3e29cafa
2024-08-13 04:30:00
@ 76c71aae:3e29cafa
2024-08-13 04:30:00On social media and in the Nostr space in particular, there’s been a lot of debate about the idea of supporting deletion and editing of notes.
Some people think they’re vital features to have, others believe that more honest and healthy social media will come from getting rid of these features. The discussion about these features quickly turns to the feasibility of completely deleting something on a decentralized protocol. We quickly get to the “We can’t really delete anything from the internet, or a decentralized network.” argument. This crowds out how Delete and Edit can mimic elements of offline interactions, how they can be used as social signals.
When it comes to issues of deletion and editing content, what matters more is if the creator can communicate their intentions around their content. Sure, on the internet, with decentralized protocols, there’s no way to be sure something’s deleted. It’s not like taking a piece of paper and burning it. Computers make copies of things all the time, computers don’t like deleting things. In particular, distributed systems tend to use a Kafka architecture with immutable logs, it’s just easier to keep everything around, as deleting and reindexing is hard. Even if the software could be made to delete something, there’s always screenshots, or even pictures of screens. We can’t provably make something disappear.
What we need to do in our software is clearly express intention. A delete is actually a kind of retraction. “I no longer want to associate myself with this content, please stop showing it to people as part of what I’ve published, stop highlighting it, stop sharing it.” Even if a relay or other server keeps a copy, and keeps sharing it, being able to clearly state “hello world, this thing I said, was a mistake, please get rid of it.” Just giving users the chance to say “I deleted this” is a way of showing intention. It’s also a way of signaling that feedback has been heard. Perhaps the post was factually incorrect or perhaps it was mean and the person wants to remove what they said. In an IRL conversation, for either of these scenarios there is some dialogue where the creator of the content is learning something and taking action based on what they’ve learned.
Without delete or edit, there is no option to signal to the rest of the community that you have learned something because of how the content is structured today. On most platforms a reply or response stating one’s learning will be lost often in a deluge of replies on the original post and subsequent posts are often not seen especially when the original goes viral. By providing tools like delete and edit we give people a chance to signal that they have heard the feedback and taken action.
The Nostr Protocol supports delete and expiring notes. It was one of the reasons we switched from secure scuttlebutt to build on Nostr. Our nos.social app offers delete and while we know that not all relays will honor this, we believe it’s important to provide social signaling tools as a means of making the internet more humane.
We believe that the power to learn from each other is more important than the need to police through moral outrage which is how the current platforms and even some Nostr clients work today.
It’s important that we don’t say Nostr doesn’t support delete. Not all apps need to support requesting a delete, some might want to call it a retraction. It is important that users know there is no way to enforce a delete and not all relays may honor their request.
Edit is similar, although not as widely supported as delete. It’s a creator making a clear statement that they’ve created a new version of their content. Maybe it’s a spelling error, or a new version of the content, or maybe they’re changing it altogether. Freedom online means freedom to retract a statement, freedom to update a statement, freedom to edit your own content. By building on these freedoms, we’ll make Nostr a space where people feel empowered and in control of their own media.
-
 @ 91bea5cd:1df4451c
2025-02-04 17:24:50
@ 91bea5cd:1df4451c
2025-02-04 17:24:50Definição de ULID:
Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível.
Gerar ULID
```sql
CREATE EXTENSION IF NOT EXISTS pgcrypto;
CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\000\000\000\000\000\000'; output TEXT = '';
unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER);
-- 10 entropy bytes ulid = timestamp || gen_random_bytes(10);
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ```
ULID TO UUID
```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF;
v = regexp_split_to_array(ulid, '');
-- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]);
-- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]);
RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE;
CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ```
UUID to ULID
```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ```
Gera 11 Digitos aleatórios: YBKXG0CKTH4
```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto;
-- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT;
-- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars;END; $$ LANGUAGE plpgsql; ```
Exemplo de USO
```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL );
-- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ```
Fontes
- https://github.com/scoville/pgsql-ulid
- https://github.com/geckoboard/pgulid
-
 @ dbb19ae0:c3f22d5a
2025-02-08 15:06:44
@ dbb19ae0:c3f22d5a
2025-02-08 15:06:44PS C:\Users\Alashazam> cortex run tinyllama In order to exit, type
exit()give me a little sentence of 10 words "Certainly, here's a little sentence of 10 words that exemplifies the power of words: 'The beauty of life is that it has the power to change us, even in the smallest ways.'" now use SQL to insert this sentence into a table that has 2 fields Id, and sentence Here's an SQL query to insert the sentence you gave into the
sentencetable:INSERT INTO sentence (id, sentence) VALUES (1, 'The beauty of life is that it has the power to change us, even in the smallest ways.');This query will create a new row in the
sentencetable with the givenidandsentence, and will also update thesentencetable'ssentencecolumn to contain the new sentence.please generate the table creation for sqlite Here's a table creation statement for a
sentencetable in SQLite:CREATE TABLE IF NOT EXISTS sentence ( id INTEGER PRIMARY KEY, sentence TEXT UNIQUE NOT NULL );This will create a table called
sentencewith the following columns:id: An integer primary key column used to uniquely identify each row.sentence: A text column containing the actual sentence.
This table will store the sentence you provided in your text input.
exit()
-
 @ 472f440f:5669301e
2024-09-12 03:17:07
@ 472f440f:5669301e
2024-09-12 03:17:07TAPS SIGN
"There is no industry in the world that is more ruthlessly competitive than the bitcoin mining industry."
From any angle you cut it the bitcoin mining economic landscape is absolutely BRUTAL at the moment. Hashprice is sitting right above an all time low at $0.04/TH/day. Yesterday brought with it yet another new difficulty all time high. Competition for energy resources is as fierce as it has ever been as rack space continues to be tight in the United States and hoards of AI data centers move in to scoop up as much power as possible.
To make matters worse, with current economics it doesn't really make sense to buy bitcoin mining machines at their current prices. The pay back period on machines is absurd considering where we find ourselves in the market. Adam O from Upstream Data broke it down in a tweet earlier today.
As he says, it probably makes more sense to buy used machines than new machines right now if you are looking to make back your money on a reasonable timeline. The only reasons you would buy new hardware right now is if you believe the price is going to rip in the near term (risky bet), you think hashrate is going to come off the network (risky bet), or if you have obscenely low power costs (unlikely for most).
If you have machines plugged in or are thinking about plugging them in soon you better be running firmware that enables you to run your machines more efficiently to increase margins. With current economics, I would make the argument that it is incredibly irresponsible to be running your machines using stock firmware. Especially if you are operating a miner in the public markets or are a private miner backed by investors. It is a disservice to your shareholders. This is a strategy we have been deploying at Cathedra for years now and it has helped us to survive during these trying times in the mining industry and set us up to successfully complete a strategic merger with Kungsleden at an opportune time.
On that note, this is a trend you can expect to pick up over the next six months; mergers and acquisitions. We wrote earlier this year that M&A activity would pick up after the halving began to eat into the economics of mining businesses and that is exactly what is happening. We decided to move early at Cathedra to get ahead of the curve. Since then Cleanspark announced a merger with GRIID, Riot has initiated an attempted hostile takeover of Bitfarms, Bitfarms has entered an agreement to merge with Stronghold, and Terawulf has signaled that they are open to a merger if a particular deal makes sense. On top of this, Rhodium slipped into bankruptcy last month. As margins continue to be squeezed and companies get more desperate I expect this type of consolidation to accelerate.
All signs are pointing toward more pain in the world of mining in the near term. There is nothing outside of a face ripping rally in the price of bitcoin or some unforeseen event that knocks out a material amount of hashrate that will change this reality. Especially considering the fact that Bitmain announced a new hydro model that will produce 860 TH/s at ~13 J/TH! This will be the highest hashing, most energy efficient machine to ever hit the market by a considerable margin.
Once these machines hit the market (if they haven't already via Bitmain plugging them in, which could explain new difficulty all time highs despite terrible mining conditions) every other machine on the market is going to suffer economically.
To make matters worse for everyone struggling right now, savvy energy producers are beginning to understand the benefits bitcoin mining can bring to their operational stack. Japanese energy giant TEPCO is reportedly planning to scale up their mining operations after beginning pilots in late 2022. They want to utilize the excess energy produced by renewable sources to mine bitcoin. From what I can tell, they haven't scaled up significantly yet. However, it is reasonable to believe that they will scale up and other energy producers will take notice. Pushing the industry closer to its inevitable end state; vertical integration via energy producers who have the lowest cost of production.
Thank you for coming to my TED Talk. Keep hashing if you can.
Final thought...
The pets need protecting.
-
 @ d076d4cc:e8d8f919
2025-02-08 12:04:00
@ d076d4cc:e8d8f919
2025-02-08 12:04:00Betano là một nền tảng kỹ thuật số tiên tiến, được thiết kế để mang đến trải nghiệm mượt mà và hiện đại cho người dùng. Với giao diện thân thiện, trực quan và dễ sử dụng, Betano cho phép người dùng thao tác một cách nhanh chóng và thuận tiện trên nhiều thiết bị khác nhau. Nền tảng này không ngừng tối ưu hóa để đảm bảo hiệu suất cao, giúp mọi hoạt động diễn ra ổn định và không bị gián đoạn. Đây là yếu tố quan trọng giúp Betano trở thành sự lựa chọn hàng đầu trong lĩnh vực kỹ thuật số.
Yếu tố bảo mật luôn được BETANO đặt lên hàng đầu nhằm đảm bảo sự an toàn tuyệt đối cho người dùng. Hệ thống bảo mật đa lớp được tích hợp để bảo vệ thông tin cá nhân cũng như dữ liệu quan trọng, ngăn chặn mọi nguy cơ rủi ro. Công nghệ mã hóa hiện đại giúp đảm bảo rằng tất cả thông tin đều được bảo vệ một cách nghiêm ngặt. Betano cũng thường xuyên cập nhật và nâng cấp hệ thống bảo mật để đáp ứng các tiêu chuẩn cao nhất, mang đến sự an tâm tuyệt đối cho người dùng.
Bên cạnh yếu tố bảo mật, Betano còn đặc biệt chú trọng đến hiệu suất hoạt động của nền tảng. Hệ thống được thiết kế để đảm bảo tốc độ xử lý nhanh, giúp người dùng dễ dàng truy cập và sử dụng mà không gặp lỗi kỹ thuật. Những tính năng tiên tiến được cập nhật liên tục nhằm nâng cao trải nghiệm tổng thể, mang đến sự thuận tiện và hài lòng tối đa. Betano luôn hướng đến việc tạo ra một nền tảng kỹ thuật số linh hoạt, dễ sử dụng và phù hợp với mọi đối tượng người dùng.
Dịch vụ chăm sóc khách hàng của Betano được đánh giá cao nhờ sự tận tâm và chuyên nghiệp. Đội ngũ hỗ trợ hoạt động 24/7, luôn sẵn sàng giải đáp mọi thắc mắc và xử lý các vấn đề một cách nhanh chóng, hiệu quả. Người dùng có thể liên hệ với bộ phận chăm sóc khách hàng thông qua nhiều kênh khác nhau để nhận được sự hỗ trợ tốt nhất. Đây chính là một trong những điểm mạnh giúp Betano tạo dựng được lòng tin và sự hài lòng từ cộng đồng người dùng.
Với sự kết hợp giữa công nghệ hiện đại, hệ thống bảo mật tiên tiến và dịch vụ chăm sóc khách hàng chuyên nghiệp, Betano không ngừng khẳng định vị thế của mình trong lĩnh vực kỹ thuật số. Những cải tiến liên tục giúp nền tảng này đáp ứng nhu cầu ngày càng đa dạng của người dùng, mang đến trải nghiệm hoàn hảo và đáng tin cậy.
-
 @ 3bf0c63f:aefa459d
2024-01-14 14:52:16
@ 3bf0c63f:aefa459d
2024-01-14 14:52:16Drivechain
Understanding Drivechain requires a shift from the paradigm most bitcoiners are used to. It is not about "trustlessness" or "mathematical certainty", but game theory and incentives. (Well, Bitcoin in general is also that, but people prefer to ignore it and focus on some illusion of trustlessness provided by mathematics.)
Here we will describe the basic mechanism (simple) and incentives (complex) of "hashrate escrow" and how it enables a 2-way peg between the mainchain (Bitcoin) and various sidechains.
The full concept of "Drivechain" also involves blind merged mining (i.e., the sidechains mine themselves by publishing their block hashes to the mainchain without the miners having to run the sidechain software), but this is much easier to understand and can be accomplished either by the BIP-301 mechanism or by the Spacechains mechanism.
How does hashrate escrow work from the point of view of Bitcoin?
A new address type is created. Anything that goes in that is locked and can only be spent if all miners agree on the Withdrawal Transaction (
WT^) that will spend it for 6 months. There is one of these special addresses for each sidechain.To gather miners' agreement
bitcoindkeeps track of the "score" of all transactions that could possibly spend from that address. On every block mined, for each sidechain, the miner can use a portion of their coinbase to either increase the score of oneWT^by 1 while decreasing the score of all others by 1; or they can decrease the score of allWT^s by 1; or they can do nothing.Once a transaction has gotten a score high enough, it is published and funds are effectively transferred from the sidechain to the withdrawing users.
If a timeout of 6 months passes and the score doesn't meet the threshold, that
WT^is discarded.What does the above procedure mean?
It means that people can transfer coins from the mainchain to a sidechain by depositing to the special address. Then they can withdraw from the sidechain by making a special withdraw transaction in the sidechain.
The special transaction somehow freezes funds in the sidechain while a transaction that aggregates all withdrawals into a single mainchain
WT^, which is then submitted to the mainchain miners so they can start voting on it and finally after some months it is published.Now the crucial part: the validity of the
WT^is not verified by the Bitcoin mainchain rules, i.e., if Bob has requested a withdraw from the sidechain to his mainchain address, but someone publishes a wrongWT^that instead takes Bob's funds and sends them to Alice's main address there is no way the mainchain will know that. What determines the "validity" of theWT^is the miner vote score and only that. It is the job of miners to vote correctly -- and for that they may want to run the sidechain node in SPV mode so they can attest for the existence of a reference to theWT^transaction in the sidechain blockchain (which then ensures it is ok) or do these checks by some other means.What? 6 months to get my money back?
Yes. But no, in practice anyone who wants their money back will be able to use an atomic swap, submarine swap or other similar service to transfer funds from the sidechain to the mainchain and vice-versa. The long delayed withdraw costs would be incurred by few liquidity providers that would gain some small profit from it.
Why bother with this at all?
Drivechains solve many different problems:
It enables experimentation and new use cases for Bitcoin
Issued assets, fully private transactions, stateful blockchain contracts, turing-completeness, decentralized games, some "DeFi" aspects, prediction markets, futarchy, decentralized and yet meaningful human-readable names, big blocks with a ton of normal transactions on them, a chain optimized only for Lighting-style networks to be built on top of it.
These are some ideas that may have merit to them, but were never actually tried because they couldn't be tried with real Bitcoin or inferfacing with real bitcoins. They were either relegated to the shitcoin territory or to custodial solutions like Liquid or RSK that may have failed to gain network effect because of that.
It solves conflicts and infighting
Some people want fully private transactions in a UTXO model, others want "accounts" they can tie to their name and build reputation on top; some people want simple multisig solutions, others want complex code that reads a ton of variables; some people want to put all the transactions on a global chain in batches every 10 minutes, others want off-chain instant transactions backed by funds previously locked in channels; some want to spend, others want to just hold; some want to use blockchain technology to solve all the problems in the world, others just want to solve money.
With Drivechain-based sidechains all these groups can be happy simultaneously and don't fight. Meanwhile they will all be using the same money and contributing to each other's ecosystem even unwillingly, it's also easy and free for them to change their group affiliation later, which reduces cognitive dissonance.
It solves "scaling"
Multiple chains like the ones described above would certainly do a lot to accomodate many more transactions that the current Bitcoin chain can. One could have special Lightning Network chains, but even just big block chains or big-block-mimblewimble chains or whatnot could probably do a good job. Or even something less cool like 200 independent chains just like Bitcoin is today, no extra features (and you can call it "sharding"), just that would already multiply the current total capacity by 200.
Use your imagination.
It solves the blockchain security budget issue
The calculation is simple: you imagine what security budget is reasonable for each block in a world without block subsidy and divide that for the amount of bytes you can fit in a single block: that is the price to be paid in satoshis per byte. In reasonable estimative, the price necessary for every Bitcoin transaction goes to very large amounts, such that not only any day-to-day transaction has insanely prohibitive costs, but also Lightning channel opens and closes are impracticable.
So without a solution like Drivechain you'll be left with only one alternative: pushing Bitcoin usage to trusted services like Liquid and RSK or custodial Lightning wallets. With Drivechain, though, there could be thousands of transactions happening in sidechains and being all aggregated into a sidechain block that would then pay a very large fee to be published (via blind merged mining) to the mainchain. Bitcoin security guaranteed.
It keeps Bitcoin decentralized
Once we have sidechains to accomodate the normal transactions, the mainchain functionality can be reduced to be only a "hub" for the sidechains' comings and goings, and then the maximum block size for the mainchain can be reduced to, say, 100kb, which would make running a full node very very easy.
Can miners steal?
Yes. If a group of coordinated miners are able to secure the majority of the hashpower and keep their coordination for 6 months, they can publish a
WT^that takes the money from the sidechains and pays to themselves.Will miners steal?
No, because the incentives are such that they won't.
Although it may look at first that stealing is an obvious strategy for miners as it is free money, there are many costs involved:
- The cost of ceasing blind-merged mining returns -- as stealing will kill a sidechain, all the fees from it that miners would be expected to earn for the next years are gone;
- The cost of Bitcoin price going down: If a steal is successful that will mean Drivechains are not safe, therefore Bitcoin is less useful, and miner credibility will also be hurt, which are likely to cause the Bitcoin price to go down, which in turn may kill the miners' businesses and savings;
- The cost of coordination -- assuming miners are just normal businesses, they just want to do their work and get paid, but stealing from a Drivechain will require coordination with other miners to conduct an immoral act in a way that has many pitfalls and is likely to be broken over the months;
- The cost of miners leaving your mining pool: when we talked about "miners" above we were actually talking about mining pools operators, so they must also consider the risk of miners migrating from their mining pool to others as they begin the process of stealing;
- The cost of community goodwill -- when participating in a steal operation, a miner will suffer a ton of backlash from the community. Even if the attempt fails at the end, the fact that it was attempted will contribute to growing concerns over exaggerated miners power over the Bitcoin ecosystem, which may end up causing the community to agree on a hard-fork to change the mining algorithm in the future, or to do something to increase participation of more entities in the mining process (such as development or cheapment of new ASICs), which have a chance of decreasing the profits of current miners.
Another point to take in consideration is that one may be inclined to think a newly-created sidechain or a sidechain with relatively low usage may be more easily stolen from, since the blind merged mining returns from it (point 1 above) are going to be small -- but the fact is also that a sidechain with small usage will also have less money to be stolen from, and since the other costs besides 1 are less elastic at the end it will not be worth stealing from these too.
All of the above consideration are valid only if miners are stealing from good sidechains. If there is a sidechain that is doing things wrong, scamming people, not being used at all, or is full of bugs, for example, that will be perceived as a bad sidechain, and then miners can and will safely steal from it and kill it, which will be perceived as a good thing by everybody.
What do we do if miners steal?
Paul Sztorc has suggested in the past that a user-activated soft-fork could prevent miners from stealing, i.e., most Bitcoin users and nodes issue a rule similar to this one to invalidate the inclusion of a faulty
WT^and thus cause any miner that includes it in a block to be relegated to their own Bitcoin fork that other nodes won't accept.This suggestion has made people think Drivechain is a sidechain solution backed by user-actived soft-forks for safety, which is very far from the truth. Drivechains must not and will not rely on this kind of soft-fork, although they are possible, as the coordination costs are too high and no one should ever expect these things to happen.
If even with all the incentives against them (see above) miners do still steal from a good sidechain that will mean the failure of the Drivechain experiment. It will very likely also mean the failure of the Bitcoin experiment too, as it will be proven that miners can coordinate to act maliciously over a prolonged period of time regardless of economic and social incentives, meaning they are probably in it just for attacking Bitcoin, backed by nation-states or something else, and therefore no Bitcoin transaction in the mainchain is to be expected to be safe ever again.
Why use this and not a full-blown trustless and open sidechain technology?
Because it is impossible.
If you ever heard someone saying "just use a sidechain", "do this in a sidechain" or anything like that, be aware that these people are either talking about "federated" sidechains (i.e., funds are kept in custody by a group of entities) or they are talking about Drivechain, or they are disillusioned and think it is possible to do sidechains in any other manner.
No, I mean a trustless 2-way peg with correctness of the withdrawals verified by the Bitcoin protocol!
That is not possible unless Bitcoin verifies all transactions that happen in all the sidechains, which would be akin to drastically increasing the blocksize and expanding the Bitcoin rules in tons of ways, i.e., a terrible idea that no one wants.
What about the Blockstream sidechains whitepaper?
Yes, that was a way to do it. The Drivechain hashrate escrow is a conceptually simpler way to achieve the same thing with improved incentives, less junk in the chain, more safety.
Isn't the hashrate escrow a very complex soft-fork?
Yes, but it is much simpler than SegWit. And, unlike SegWit, it doesn't force anything on users, i.e., it isn't a mandatory blocksize increase.
Why should we expect miners to care enough to participate in the voting mechanism?
Because it's in their own self-interest to do it, and it costs very little. Today over half of the miners mine RSK. It's not blind merged mining, it's a very convoluted process that requires them to run a RSK full node. For the Drivechain sidechains, an SPV node would be enough, or maybe just getting data from a block explorer API, so much much simpler.
What if I still don't like Drivechain even after reading this?
That is the entire point! You don't have to like it or use it as long as you're fine with other people using it. The hashrate escrow special addresses will not impact you at all, validation cost is minimal, and you get the benefit of people who want to use Drivechain migrating to their own sidechains and freeing up space for you in the mainchain. See also the point above about infighting.
See also
-
 @ 91bea5cd:1df4451c
2025-02-04 17:15:57
@ 91bea5cd:1df4451c
2025-02-04 17:15:57Definição de ULID:
Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível.
Gerar ULID
```sql
CREATE EXTENSION IF NOT EXISTS pgcrypto;
CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\000\000\000\000\000\000'; output TEXT = '';
unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER);
-- 10 entropy bytes ulid = timestamp || gen_random_bytes(10);
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ```
ULID TO UUID
```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF;
v = regexp_split_to_array(ulid, '');
-- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]);
-- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]);
RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE;
CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ```
UUID to ULID
```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ```
Gera 11 Digitos aleatórios: YBKXG0CKTH4
```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto;
-- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT;
-- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars;END; $$ LANGUAGE plpgsql; ```
Exemplo de USO
```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL );
-- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ```
Fontes
- https://github.com/scoville/pgsql-ulid
- https://github.com/geckoboard/pgulid
-
 @ e5272de9:a16a102f
2024-09-10 19:13:30
@ e5272de9:a16a102f
2024-09-10 19:13:30What is the Grapevine?
The Grapevine enables you and your community to identify who is the most trustworthy, and in what context, to curate content, facts, and information.
In this article we present an overview of the Grapevine Worldview, a visualization tool and control panel for the management of your grapevine.
How does the grapevine work?
The construction of a Grapevine Worldview can be broken down into the following steps:
Step 1. Decide what question you want to answer or the problem you want to solve. For example: curate a directory of nostr apps. The finished product will be a ranked list, G, of items that may be pubkeys or could be something else, e.g. products from an eCommerce site.
Step 2. Select whatever sources of raw data (usually from within nostr, but in theory, could come from outside nostr) that are both 1) available to you and 2) relevant to the question or problem. (See Table: Sources of Raw Data at [1].)
Step 3. Translate each data source into a format suitable for consumption by the grapevine through the process of interpretation (see [1]).
Step 4. Crunch the numbers using the GrapeRank equations. Each purple arrow in the Worldview represents a single iteration. If the arrow loops around in a circle, iterations repeat until convergence. The finished product will be a list G of items, ranked by GrapeRank score.
Step 5: Consume the list G in whatever way you see fit. If the product is a ranked list of pubkeys, it may be used to curate a feed or you may use it as part of the curation process within other Worldviews.
The Worldview is designed to give a big picture overview of the entire above process. In this post I will walk though a simple example of a hypothetical Grapevine Worldview, designed around the problem of how to curate a list of nostr apps.
Example Worldview: Curation of Nostr Apps
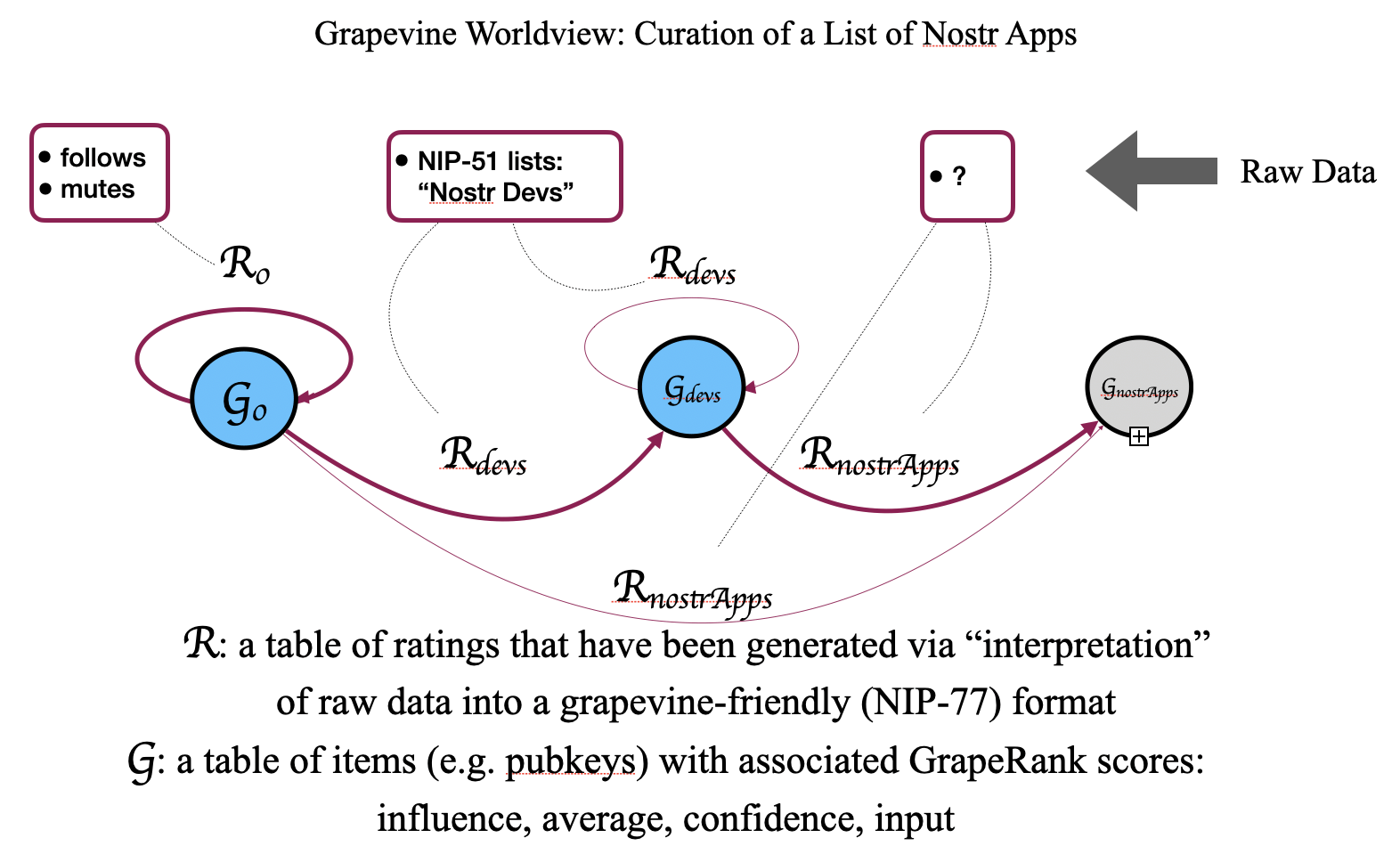
The Worldview in the above figure is designed for a specific purpose: to manage a list of nostr apps. [2]
Each node G on the worldview represents a table of items, each of which is associated with a contextual GrapeRank score, calculated using the GrapeRank algorithm. The blue nodes represent tables of pubkeys, and the grey node represents a list of non-pubkey items, in this case the list of nostr apps.
Each edge (purple arrow) is associated with an array R of ratings r, each of which must follow the Grapevine Ratings format. Each R is generated from raw ratings data that can be from any source, in any format. Multiple categories of data can be merged into a single dataset R. For each R, and for each category of raw data that contributes to R, an explicit Interpretation must be provided.
If we look from left to right in the above figure, we can see information processed through the following stages:
Stage 1: Follows and mutes (raw ratings data) is used to curate G_o: a table of pubkeys that are (probably) not bots or other bad actors
Stage 2: NIP-51 lists entitled "Nostr Devs" (raw data) is used to curate G_devs. Note that authors of these lists are filtered and weighted using G_o from the previous stage.
Stage 3: Content authored by G_devs is used to curate G_nostrApps, the list of Nost Apps.
The source of potential items to initialize the list G_nostrApps is unspecified in the worldview, but one possibility would be to make use of Nostr forms, as seen at formstr.
The content used to initialized R_nostrApps used in stage 3 is also left unspecified. One possibility would be to use NIP-32 labels to endorse submitted items as belonging / not belonging on the list. Anyone could submit labels, but only pubkeys represented in G_0 or G_devs will be given a voice, and that voice will be proportional to that pubkey's influence score. The relative thickness of the two purple arrows leading to the G_nostrApps node on the right tells us that nostr developers are given a louder voice in the final curation of G_nostrApps.
Values and choices of the end-user
The Grapevine Worldview places the values and choices of the end user center stage. These choices are manifest in several ways: * the choice of raw data: what is included, what data is available but ignored * the specifics of the interpretation of each category of raw data into a list R of individual ratings r * the overall topology of the Worldview, including the choices of which G's to incorporate * the demonstrated willingness to expend computational energy on any given aspects of the above. For now, the computational energy will be trivial. At some point, the energy expenditure will have a nontrivial cost.
Summary
The Grapevine Worldview is a visual overview and a control panel for the process leading up to the curation of some category of content by your grapevine. Construction of any given worldview includes decisions on who should be trusted to curate what. These decisions may or may not be the same from one end user to another.
Each user can manage multiple Worldviews, each one of which is purposed for the curation of a given G. And the output of one Worldview, G, can be consumed by a different Worldview.
Current efforts are directed at creating an open source library for the GrapeRank equations. Next step will be back end services that partner with relays and will enable generation of G_0, the Grapevine Network of "not-bot" pubkeys. We anticipate that future work will build out the front end control panel for Worldviews, including control panels for the interpretation of additional data sources and curation of lists like nostr apps as in the example above.
Notes
[1] https://njump.me / naddr1qvzqqqr4gupzpef89h53f0fsza2ugwdc3e54nfpun5nxfqclpy79r6w8nxsk5yp0qqxnzdejx5urzwp58qcrgdp4dutxqa
[2] Currently, various lists of nostr apps are maintained, e.g. at Awesome Nostr by (Aljaz Ceru?), or at nostrapps.com by (Karnage?).
-
 @ b17fccdf:b7211155
2025-01-21 17:02:21
@ b17fccdf:b7211155
2025-01-21 17:02:21The past 26 August, Tor introduced officially a proof-of-work (PoW) defense for onion services designed to prioritize verified network traffic as a deterrent against denial of service (DoS) attacks.
~ > This feature at the moment, is deactivate by default, so you need to follow these steps to activate this on a MiniBolt node:
- Make sure you have the latest version of Tor installed, at the time of writing this post, which is v0.4.8.6. Check your current version by typing
tor --versionExample of expected output:
Tor version 0.4.8.6. This build of Tor is covered by the GNU General Public License (https://www.gnu.org/licenses/gpl-3.0.en.html) Tor is running on Linux with Libevent 2.1.12-stable, OpenSSL 3.0.9, Zlib 1.2.13, Liblzma 5.4.1, Libzstd N/A and Glibc 2.36 as libc. Tor compiled with GCC version 12.2.0~ > If you have v0.4.8.X, you are OK, if not, type
sudo apt update && sudo apt upgradeand confirm to update.- Basic PoW support can be checked by running this command:
tor --list-modulesExpected output:
relay: yes dirauth: yes dircache: yes pow: **yes**~ > If you have
pow: yes, you are OK- Now go to the torrc file of your MiniBolt and add the parameter to enable PoW for each hidden service added
sudo nano /etc/tor/torrcExample:
```
Hidden Service BTC RPC Explorer
HiddenServiceDir /var/lib/tor/hidden_service_btcrpcexplorer/ HiddenServiceVersion 3 HiddenServicePoWDefensesEnabled 1 HiddenServicePort 80 127.0.0.1:3002 ```
~ > Bitcoin Core and LND use the Tor control port to automatically create the hidden service, requiring no action from the user. We have submitted a feature request in the official GitHub repositories to explore the need for the integration of Tor's PoW defense into the automatic creation process of the hidden service. You can follow them at the following links:
- Bitcoin Core: https://github.com/lightningnetwork/lnd/issues/8002
- LND: https://github.com/bitcoin/bitcoin/issues/28499
More info:
- https://blog.torproject.org/introducing-proof-of-work-defense-for-onion-services/
- https://gitlab.torproject.org/tpo/onion-services/onion-support/-/wikis/Documentation/PoW-FAQ
Enjoy it MiniBolter! 💙
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Personagens de jogos e símbolos
A sensação de "ser" um personagem em um jogo ou uma brincadeira talvez seja o mais próximo que eu tenha conseguido chegar do entendimento de um símbolo religioso.
A hóstia consagrada é, segundo a religião, o corpo de Cristo, mas nossa mente moderna só consegue concebê-la como sendo uma representação do corpo de Cristo. Da mesma forma outras culturas e outras religiões têm símbolos parecidos, inclusive nos quais o próprio participante do ritual faz o papel de um deus ou de qualquer coisa parecida.
"Faz o papel" é de novo a interpretação da mente moderna. O sujeito ali é a coisa, mas ele ao mesmo tempo que é também sabe que não é, que continua sendo ele mesmo.
Nos jogos de videogame e brincadeiras infantis em que se encarna um personagem o jogador é o personagem. não se diz, entre os jogadores, que alguém está "encenando", mas que ele é e pronto. nem há outra denominação ou outro verbo. No máximo "encarnando", mas já aí já é vocabulário jornalístico feito para facilitar a compreensão de quem está de fora do jogo.
-
 @ 6be5cc06:5259daf0
2025-01-21 01:51:46
@ 6be5cc06:5259daf0
2025-01-21 01:51:46Bitcoin: Um sistema de dinheiro eletrônico direto entre pessoas.
Satoshi Nakamoto
satoshin@gmx.com
www.bitcoin.org
Resumo
O Bitcoin é uma forma de dinheiro digital que permite pagamentos diretos entre pessoas, sem a necessidade de um banco ou instituição financeira. Ele resolve um problema chamado gasto duplo, que ocorre quando alguém tenta gastar o mesmo dinheiro duas vezes. Para evitar isso, o Bitcoin usa uma rede descentralizada onde todos trabalham juntos para verificar e registrar as transações.
As transações são registradas em um livro público chamado blockchain, protegido por uma técnica chamada Prova de Trabalho. Essa técnica cria uma cadeia de registros que não pode ser alterada sem refazer todo o trabalho já feito. Essa cadeia é mantida pelos computadores que participam da rede, e a mais longa é considerada a verdadeira.
Enquanto a maior parte do poder computacional da rede for controlada por participantes honestos, o sistema continuará funcionando de forma segura. A rede é flexível, permitindo que qualquer pessoa entre ou saia a qualquer momento, sempre confiando na cadeia mais longa como prova do que aconteceu.
1. Introdução
Hoje, quase todos os pagamentos feitos pela internet dependem de bancos ou empresas como processadores de pagamento (cartões de crédito, por exemplo) para funcionar. Embora esse sistema seja útil, ele tem problemas importantes porque é baseado em confiança.
Primeiro, essas empresas podem reverter pagamentos, o que é útil em caso de erros, mas cria custos e incertezas. Isso faz com que pequenas transações, como pagar centavos por um serviço, se tornem inviáveis. Além disso, os comerciantes são obrigados a desconfiar dos clientes, pedindo informações extras e aceitando fraudes como algo inevitável.
Esses problemas não existem no dinheiro físico, como o papel-moeda, onde o pagamento é final e direto entre as partes. No entanto, não temos como enviar dinheiro físico pela internet sem depender de um intermediário confiável.
O que precisamos é de um sistema de pagamento eletrônico baseado em provas matemáticas, não em confiança. Esse sistema permitiria que qualquer pessoa enviasse dinheiro diretamente para outra, sem depender de bancos ou processadores de pagamento. Além disso, as transações seriam irreversíveis, protegendo vendedores contra fraudes, mas mantendo a possibilidade de soluções para disputas legítimas.
Neste documento, apresentamos o Bitcoin, que resolve o problema do gasto duplo usando uma rede descentralizada. Essa rede cria um registro público e protegido por cálculos matemáticos, que garante a ordem das transações. Enquanto a maior parte da rede for controlada por pessoas honestas, o sistema será seguro contra ataques.
2. Transações
Para entender como funciona o Bitcoin, é importante saber como as transações são realizadas. Imagine que você quer transferir uma "moeda digital" para outra pessoa. No sistema do Bitcoin, essa "moeda" é representada por uma sequência de registros que mostram quem é o atual dono. Para transferi-la, você adiciona um novo registro comprovando que agora ela pertence ao próximo dono. Esse registro é protegido por um tipo especial de assinatura digital.
O que é uma assinatura digital?
Uma assinatura digital é como uma senha secreta, mas muito mais segura. No Bitcoin, cada usuário tem duas chaves: uma "chave privada", que é secreta e serve para criar a assinatura, e uma "chave pública", que pode ser compartilhada com todos e é usada para verificar se a assinatura é válida. Quando você transfere uma moeda, usa sua chave privada para assinar a transação, provando que você é o dono. A próxima pessoa pode usar sua chave pública para confirmar isso.
Como funciona na prática?
Cada "moeda" no Bitcoin é, na verdade, uma cadeia de assinaturas digitais. Vamos imaginar o seguinte cenário:
- A moeda está com o Dono 0 (você). Para transferi-la ao Dono 1, você assina digitalmente a transação com sua chave privada. Essa assinatura inclui o código da transação anterior (chamado de "hash") e a chave pública do Dono 1.
- Quando o Dono 1 quiser transferir a moeda ao Dono 2, ele assinará a transação seguinte com sua própria chave privada, incluindo também o hash da transação anterior e a chave pública do Dono 2.
- Esse processo continua, formando uma "cadeia" de transações. Qualquer pessoa pode verificar essa cadeia para confirmar quem é o atual dono da moeda.
Resolvendo o problema do gasto duplo
Um grande desafio com moedas digitais é o "gasto duplo", que é quando uma mesma moeda é usada em mais de uma transação. Para evitar isso, muitos sistemas antigos dependiam de uma entidade central confiável, como uma casa da moeda, que verificava todas as transações. No entanto, isso criava um ponto único de falha e centralizava o controle do dinheiro.
O Bitcoin resolve esse problema de forma inovadora: ele usa uma rede descentralizada onde todos os participantes (os "nós") têm acesso a um registro completo de todas as transações. Cada nó verifica se as transações são válidas e se a moeda não foi gasta duas vezes. Quando a maioria dos nós concorda com a validade de uma transação, ela é registrada permanentemente na blockchain.
Por que isso é importante?
Essa solução elimina a necessidade de confiar em uma única entidade para gerenciar o dinheiro, permitindo que qualquer pessoa no mundo use o Bitcoin sem precisar de permissão de terceiros. Além disso, ela garante que o sistema seja seguro e resistente a fraudes.
3. Servidor Timestamp
Para assegurar que as transações sejam realizadas de forma segura e transparente, o sistema Bitcoin utiliza algo chamado de "servidor de registro de tempo" (timestamp). Esse servidor funciona como um registro público que organiza as transações em uma ordem específica.
Ele faz isso agrupando várias transações em blocos e criando um código único chamado "hash". Esse hash é como uma impressão digital que representa todo o conteúdo do bloco. O hash de cada bloco é amplamente divulgado, como se fosse publicado em um jornal ou em um fórum público.
Esse processo garante que cada bloco de transações tenha um registro de quando foi criado e que ele existia naquele momento. Além disso, cada novo bloco criado contém o hash do bloco anterior, formando uma cadeia contínua de blocos conectados — conhecida como blockchain.
Com isso, se alguém tentar alterar qualquer informação em um bloco anterior, o hash desse bloco mudará e não corresponderá ao hash armazenado no bloco seguinte. Essa característica torna a cadeia muito segura, pois qualquer tentativa de fraude seria imediatamente detectada.
O sistema de timestamps é essencial para provar a ordem cronológica das transações e garantir que cada uma delas seja única e autêntica. Dessa forma, ele reforça a segurança e a confiança na rede Bitcoin.
4. Prova-de-Trabalho
Para implementar o registro de tempo distribuído no sistema Bitcoin, utilizamos um mecanismo chamado prova-de-trabalho. Esse sistema é semelhante ao Hashcash, desenvolvido por Adam Back, e baseia-se na criação de um código único, o "hash", por meio de um processo computacionalmente exigente.
A prova-de-trabalho envolve encontrar um valor especial que, quando processado junto com as informações do bloco, gere um hash que comece com uma quantidade específica de zeros. Esse valor especial é chamado de "nonce". Encontrar o nonce correto exige um esforço significativo do computador, porque envolve tentativas repetidas até que a condição seja satisfeita.
Esse processo é importante porque torna extremamente difícil alterar qualquer informação registrada em um bloco. Se alguém tentar mudar algo em um bloco, seria necessário refazer o trabalho de computação não apenas para aquele bloco, mas também para todos os blocos que vêm depois dele. Isso garante a segurança e a imutabilidade da blockchain.
A prova-de-trabalho também resolve o problema de decidir qual cadeia de blocos é a válida quando há múltiplas cadeias competindo. A decisão é feita pela cadeia mais longa, pois ela representa o maior esforço computacional já realizado. Isso impede que qualquer indivíduo ou grupo controle a rede, desde que a maioria do poder de processamento seja mantida por participantes honestos.
Para garantir que o sistema permaneça eficiente e equilibrado, a dificuldade da prova-de-trabalho é ajustada automaticamente ao longo do tempo. Se novos blocos estiverem sendo gerados rapidamente, a dificuldade aumenta; se estiverem sendo gerados muito lentamente, a dificuldade diminui. Esse ajuste assegura que novos blocos sejam criados aproximadamente a cada 10 minutos, mantendo o sistema estável e funcional.
5. Rede
A rede Bitcoin é o coração do sistema e funciona de maneira distribuída, conectando vários participantes (ou nós) para garantir o registro e a validação das transações. Os passos para operar essa rede são:
-
Transmissão de Transações: Quando alguém realiza uma nova transação, ela é enviada para todos os nós da rede. Isso é feito para garantir que todos estejam cientes da operação e possam validá-la.
-
Coleta de Transações em Blocos: Cada nó agrupa as novas transações recebidas em um "bloco". Este bloco será preparado para ser adicionado à cadeia de blocos (a blockchain).
-
Prova-de-Trabalho: Os nós competem para resolver a prova-de-trabalho do bloco, utilizando poder computacional para encontrar um hash válido. Esse processo é como resolver um quebra-cabeça matemático difícil.
-
Envio do Bloco Resolvido: Quando um nó encontra a solução para o bloco (a prova-de-trabalho), ele compartilha esse bloco com todos os outros nós na rede.
-
Validação do Bloco: Cada nó verifica o bloco recebido para garantir que todas as transações nele contidas sejam válidas e que nenhuma moeda tenha sido gasta duas vezes. Apenas blocos válidos são aceitos.
-
Construção do Próximo Bloco: Os nós que aceitaram o bloco começam a trabalhar na criação do próximo bloco, utilizando o hash do bloco aceito como base (hash anterior). Isso mantém a continuidade da cadeia.
Resolução de Conflitos e Escolha da Cadeia Mais Longa
Os nós sempre priorizam a cadeia mais longa, pois ela representa o maior esforço computacional já realizado, garantindo maior segurança. Se dois blocos diferentes forem compartilhados simultaneamente, os nós trabalharão no primeiro bloco recebido, mas guardarão o outro como uma alternativa. Caso o segundo bloco eventualmente forme uma cadeia mais longa (ou seja, tenha mais blocos subsequentes), os nós mudarão para essa nova cadeia.
Tolerância a Falhas
A rede é robusta e pode lidar com mensagens que não chegam a todos os nós. Uma transação não precisa alcançar todos os nós de imediato; basta que chegue a um número suficiente deles para ser incluída em um bloco. Da mesma forma, se um nó não receber um bloco em tempo hábil, ele pode solicitá-lo ao perceber que está faltando quando o próximo bloco é recebido.
Esse mecanismo descentralizado permite que a rede Bitcoin funcione de maneira segura, confiável e resiliente, sem depender de uma autoridade central.
6. Incentivo
O incentivo é um dos pilares fundamentais que sustenta o funcionamento da rede Bitcoin, garantindo que os participantes (nós) continuem operando de forma honesta e contribuindo com recursos computacionais. Ele é estruturado em duas partes principais: a recompensa por mineração e as taxas de transação.
Recompensa por Mineração
Por convenção, o primeiro registro em cada bloco é uma transação especial que cria novas moedas e as atribui ao criador do bloco. Essa recompensa incentiva os mineradores a dedicarem poder computacional para apoiar a rede. Como não há uma autoridade central para emitir moedas, essa é a maneira pela qual novas moedas entram em circulação. Esse processo pode ser comparado ao trabalho de garimpeiros, que utilizam recursos para colocar mais ouro em circulação. No caso do Bitcoin, o "recurso" consiste no tempo de CPU e na energia elétrica consumida para resolver a prova-de-trabalho.
Taxas de Transação
Além da recompensa por mineração, os mineradores também podem ser incentivados pelas taxas de transação. Se uma transação utiliza menos valor de saída do que o valor de entrada, a diferença é tratada como uma taxa, que é adicionada à recompensa do bloco contendo essa transação. Com o passar do tempo e à medida que o número de moedas em circulação atinge o limite predeterminado, essas taxas de transação se tornam a principal fonte de incentivo, substituindo gradualmente a emissão de novas moedas. Isso permite que o sistema opere sem inflação, uma vez que o número total de moedas permanece fixo.
Incentivo à Honestidade
O design do incentivo também busca garantir que os participantes da rede mantenham um comportamento honesto. Para um atacante que consiga reunir mais poder computacional do que o restante da rede, ele enfrentaria duas escolhas:
- Usar esse poder para fraudar o sistema, como reverter transações e roubar pagamentos.
- Seguir as regras do sistema, criando novos blocos e recebendo recompensas legítimas.
A lógica econômica favorece a segunda opção, pois um comportamento desonesto prejudicaria a confiança no sistema, diminuindo o valor de todas as moedas, incluindo aquelas que o próprio atacante possui. Jogar dentro das regras não apenas maximiza o retorno financeiro, mas também preserva a validade e a integridade do sistema.
Esse mecanismo garante que os incentivos econômicos estejam alinhados com o objetivo de manter a rede segura, descentralizada e funcional ao longo do tempo.
7. Recuperação do Espaço em Disco
Depois que uma moeda passa a estar protegida por muitos blocos na cadeia, as informações sobre as transações antigas que a geraram podem ser descartadas para economizar espaço em disco. Para que isso seja possível sem comprometer a segurança, as transações são organizadas em uma estrutura chamada "árvore de Merkle". Essa árvore funciona como um resumo das transações: em vez de armazenar todas elas, guarda apenas um "hash raiz", que é como uma assinatura compacta que representa todo o grupo de transações.
Os blocos antigos podem, então, ser simplificados, removendo as partes desnecessárias dessa árvore. Apenas a raiz do hash precisa ser mantida no cabeçalho do bloco, garantindo que a integridade dos dados seja preservada, mesmo que detalhes específicos sejam descartados.
Para exemplificar: imagine que você tenha vários recibos de compra. Em vez de guardar todos os recibos, você cria um documento e lista apenas o valor total de cada um. Mesmo que os recibos originais sejam descartados, ainda é possível verificar a soma com base nos valores armazenados.
Além disso, o espaço ocupado pelos blocos em si é muito pequeno. Cada bloco sem transações ocupa apenas cerca de 80 bytes. Isso significa que, mesmo com blocos sendo gerados a cada 10 minutos, o crescimento anual em espaço necessário é insignificante: apenas 4,2 MB por ano. Com a capacidade de armazenamento dos computadores crescendo a cada ano, esse espaço continuará sendo trivial, garantindo que a rede possa operar de forma eficiente sem problemas de armazenamento, mesmo a longo prazo.
8. Verificação de Pagamento Simplificada
É possível confirmar pagamentos sem a necessidade de operar um nó completo da rede. Para isso, o usuário precisa apenas de uma cópia dos cabeçalhos dos blocos da cadeia mais longa (ou seja, a cadeia com maior esforço de trabalho acumulado). Ele pode verificar a validade de uma transação ao consultar os nós da rede até obter a confirmação de que tem a cadeia mais longa. Para isso, utiliza-se o ramo Merkle, que conecta a transação ao bloco em que ela foi registrada.
Entretanto, o método simplificado possui limitações: ele não pode confirmar uma transação isoladamente, mas sim assegurar que ela ocupa um lugar específico na cadeia mais longa. Dessa forma, se um nó da rede aprova a transação, os blocos subsequentes reforçam essa aceitação.
A verificação simplificada é confiável enquanto a maioria dos nós da rede for honesta. Contudo, ela se torna vulnerável caso a rede seja dominada por um invasor. Nesse cenário, um atacante poderia fabricar transações fraudulentas que enganariam o usuário temporariamente até que o invasor obtivesse controle completo da rede.
Uma estratégia para mitigar esse risco é configurar alertas nos softwares de nós completos. Esses alertas identificam blocos inválidos, sugerindo ao usuário baixar o bloco completo para confirmar qualquer inconsistência. Para maior segurança, empresas que realizam pagamentos frequentes podem preferir operar seus próprios nós, reduzindo riscos e permitindo uma verificação mais direta e confiável.
9. Combinando e Dividindo Valor
No sistema Bitcoin, cada unidade de valor é tratada como uma "moeda" individual, mas gerenciar cada centavo como uma transação separada seria impraticável. Para resolver isso, o Bitcoin permite que valores sejam combinados ou divididos em transações, facilitando pagamentos de qualquer valor.
Entradas e Saídas
Cada transação no Bitcoin é composta por:
- Entradas: Representam os valores recebidos em transações anteriores.
- Saídas: Correspondem aos valores enviados, divididos entre os destinatários e, eventualmente, o troco para o remetente.
Normalmente, uma transação contém:
- Uma única entrada com valor suficiente para cobrir o pagamento.
- Ou várias entradas combinadas para atingir o valor necessário.
O valor total das saídas nunca excede o das entradas, e a diferença (se houver) pode ser retornada ao remetente como troco.
Exemplo Prático
Imagine que você tem duas entradas:
- 0,03 BTC
- 0,07 BTC
Se deseja enviar 0,08 BTC para alguém, a transação terá:
- Entrada: As duas entradas combinadas (0,03 + 0,07 BTC = 0,10 BTC).
- Saídas: Uma para o destinatário (0,08 BTC) e outra como troco para você (0,02 BTC).
Essa flexibilidade permite que o sistema funcione sem precisar manipular cada unidade mínima individualmente.
Difusão e Simplificação
A difusão de transações, onde uma depende de várias anteriores e assim por diante, não representa um problema. Não é necessário armazenar ou verificar o histórico completo de uma transação para utilizá-la, já que o registro na blockchain garante sua integridade.
10. Privacidade
O modelo bancário tradicional oferece um certo nível de privacidade, limitando o acesso às informações financeiras apenas às partes envolvidas e a um terceiro confiável (como bancos ou instituições financeiras). No entanto, o Bitcoin opera de forma diferente, pois todas as transações são publicamente registradas na blockchain. Apesar disso, a privacidade pode ser mantida utilizando chaves públicas anônimas, que desvinculam diretamente as transações das identidades das partes envolvidas.
Fluxo de Informação
- No modelo tradicional, as transações passam por um terceiro confiável que conhece tanto o remetente quanto o destinatário.
- No Bitcoin, as transações são anunciadas publicamente, mas sem revelar diretamente as identidades das partes. Isso é comparável a dados divulgados por bolsas de valores, onde informações como o tempo e o tamanho das negociações (a "fita") são públicas, mas as identidades das partes não.
Protegendo a Privacidade
Para aumentar a privacidade no Bitcoin, são adotadas as seguintes práticas:
- Chaves Públicas Anônimas: Cada transação utiliza um par de chaves diferentes, dificultando a associação com um proprietário único.
- Prevenção de Ligação: Ao usar chaves novas para cada transação, reduz-se a possibilidade de links evidentes entre múltiplas transações realizadas pelo mesmo usuário.
Riscos de Ligação
Embora a privacidade seja fortalecida, alguns riscos permanecem:
- Transações multi-entrada podem revelar que todas as entradas pertencem ao mesmo proprietário, caso sejam necessárias para somar o valor total.
- O proprietário da chave pode ser identificado indiretamente por transações anteriores que estejam conectadas.
11. Cálculos
Imagine que temos um sistema onde as pessoas (ou computadores) competem para adicionar informações novas (blocos) a um grande registro público (a cadeia de blocos ou blockchain). Este registro é como um livro contábil compartilhado, onde todos podem verificar o que está escrito.
Agora, vamos pensar em um cenário: um atacante quer enganar o sistema. Ele quer mudar informações já registradas para beneficiar a si mesmo, por exemplo, desfazendo um pagamento que já fez. Para isso, ele precisa criar uma versão alternativa do livro contábil (a cadeia de blocos dele) e convencer todos os outros participantes de que essa versão é a verdadeira.
Mas isso é extremamente difícil.
Como o Ataque Funciona
Quando um novo bloco é adicionado à cadeia, ele depende de cálculos complexos que levam tempo e esforço. Esses cálculos são como um grande quebra-cabeça que precisa ser resolvido.
- Os “bons jogadores” (nós honestos) estão sempre trabalhando juntos para resolver esses quebra-cabeças e adicionar novos blocos à cadeia verdadeira.
- O atacante, por outro lado, precisa resolver quebra-cabeças sozinho, tentando “alcançar” a cadeia honesta para que sua versão alternativa pareça válida.
Se a cadeia honesta já está vários blocos à frente, o atacante começa em desvantagem, e o sistema está projetado para que a dificuldade de alcançá-los aumente rapidamente.
A Corrida Entre Cadeias
Você pode imaginar isso como uma corrida. A cada bloco novo que os jogadores honestos adicionam à cadeia verdadeira, eles se distanciam mais do atacante. Para vencer, o atacante teria que resolver os quebra-cabeças mais rápido que todos os outros jogadores honestos juntos.
Suponha que:
- A rede honesta tem 80% do poder computacional (ou seja, resolve 8 de cada 10 quebra-cabeças).
- O atacante tem 20% do poder computacional (ou seja, resolve 2 de cada 10 quebra-cabeças).
Cada vez que a rede honesta adiciona um bloco, o atacante tem que "correr atrás" e resolver mais quebra-cabeças para alcançar.
Por Que o Ataque Fica Cada Vez Mais Improvável?
Vamos usar uma fórmula simples para mostrar como as chances de sucesso do atacante diminuem conforme ele precisa "alcançar" mais blocos:
P = (q/p)^z
- q é o poder computacional do atacante (20%, ou 0,2).
- p é o poder computacional da rede honesta (80%, ou 0,8).
- z é a diferença de blocos entre a cadeia honesta e a cadeia do atacante.
Se o atacante está 5 blocos atrás (z = 5):
P = (0,2 / 0,8)^5 = (0,25)^5 = 0,00098, (ou, 0,098%)
Isso significa que o atacante tem menos de 0,1% de chance de sucesso — ou seja, é muito improvável.
Se ele estiver 10 blocos atrás (z = 10):
P = (0,2 / 0,8)^10 = (0,25)^10 = 0,000000095, (ou, 0,0000095%).
Neste caso, as chances de sucesso são praticamente nulas.
Um Exemplo Simples
Se você jogar uma moeda, a chance de cair “cara” é de 50%. Mas se precisar de 10 caras seguidas, sua chance já é bem menor. Se precisar de 20 caras seguidas, é quase impossível.
No caso do Bitcoin, o atacante precisa de muito mais do que 20 caras seguidas. Ele precisa resolver quebra-cabeças extremamente difíceis e alcançar os jogadores honestos que estão sempre à frente. Isso faz com que o ataque seja inviável na prática.
Por Que Tudo Isso é Seguro?
- A probabilidade de sucesso do atacante diminui exponencialmente. Isso significa que, quanto mais tempo passa, menor é a chance de ele conseguir enganar o sistema.
- A cadeia verdadeira (honesta) está protegida pela força da rede. Cada novo bloco que os jogadores honestos adicionam à cadeia torna mais difícil para o atacante alcançar.
E Se o Atacante Tentar Continuar?
O atacante poderia continuar tentando indefinidamente, mas ele estaria gastando muito tempo e energia sem conseguir nada. Enquanto isso, os jogadores honestos estão sempre adicionando novos blocos, tornando o trabalho do atacante ainda mais inútil.
Assim, o sistema garante que a cadeia verdadeira seja extremamente segura e que ataques sejam, na prática, impossíveis de ter sucesso.
12. Conclusão
Propusemos um sistema de transações eletrônicas que elimina a necessidade de confiança, baseando-se em assinaturas digitais e em uma rede peer-to-peer que utiliza prova de trabalho. Isso resolve o problema do gasto duplo, criando um histórico público de transações imutável, desde que a maioria do poder computacional permaneça sob controle dos participantes honestos. A rede funciona de forma simples e descentralizada, com nós independentes que não precisam de identificação ou coordenação direta. Eles entram e saem livremente, aceitando a cadeia de prova de trabalho como registro do que ocorreu durante sua ausência. As decisões são tomadas por meio do poder de CPU, validando blocos legítimos, estendendo a cadeia e rejeitando os inválidos. Com este mecanismo de consenso, todas as regras e incentivos necessários para o funcionamento seguro e eficiente do sistema são garantidos.
Faça o download do whitepaper original em português: https://bitcoin.org/files/bitcoin-paper/bitcoin_pt_br.pdf
-
 @ 3f770d65:7a745b24
2025-01-19 21:48:49
@ 3f770d65:7a745b24
2025-01-19 21:48:49The recent shutdown of TikTok in the United States due to a potential government ban serves as a stark reminder how fragile centralized platforms truly are under the surface. While these platforms offer convenience, a more polished user experience, and connectivity, they are ultimately beholden to governments, corporations, and other authorities. This makes them vulnerable to censorship, regulation, and outright bans. In contrast, Nostr represents a shift in how we approach online communication and content sharing. Built on the principles of decentralization and user choice, Nostr cannot be banned, because it is not a platform—it is a protocol.
PROTOCOLS, NOT PLATFORMS.
At the heart of Nostr's philosophy is user choice, a feature that fundamentally sets it apart from legacy platforms. In centralized systems, the user experience is dictated by a single person or governing entity. If the platform decides to filter, censor, or ban specific users or content, individuals are left with little action to rectify the situation. They must either accept the changes or abandon the platform entirely, often at the cost of losing their social connections, their data, and their identity.
What's happening with TikTok could never happen on Nostr. With Nostr, the dynamics are completely different. Because it is a protocol, not a platform, no single entity controls the ecosystem. Instead, the protocol enables a network of applications and relays that users can freely choose from. If a particular application or relay implements policies that a user disagrees with, such as censorship, filtering, or even government enforced banning, they are not trapped or abandoned. They have the freedom to move to another application or relay with minimal effort.
THIS IS POWERFUL.
Take, for example, the case of a relay that decides to censor specific content. On a legacy platform, this would result in frustration and a loss of access for users. On Nostr, however, users can simply connect to a different relay that does not impose such restrictions. Similarly, if an application introduces features or policies that users dislike, they can migrate to a different application that better suits their preferences, all while retaining their identity and social connections.
The same principles apply to government bans and censorship. A government can ban a specific application or even multiple applications, just as it can block one relay or several relays. China has implemented both tactics, yet Chinese users continue to exist and actively participate on Nostr, demonstrating Nostr's ability to resistant censorship.
How? Simply, it turns into a game of whack-a-mole. When one relay is censored, another quickly takes its place. When one application is banned, another emerges. Users can also bypass these obstacles by running their own relays and applications directly from their homes or personal devices, eliminating reliance on larger entities or organizations and ensuring continuous access.
AGAIN, THIS IS POWERUFL.
Nostr's open and decentralized design makes it resistant to the kinds of government intervention that led to TikTok's outages this weekend and potential future ban in the next 90 days. There is no central server to target, no company to regulate, and no single point of failure. (Insert your CEO jokes here). As long as there are individuals running relays and applications, users continue creating notes and sending zaps.
Platforms like TikTok can be silenced with the stroke of a pen, leaving millions of users disconnected and abandoned. Social communication should not be silenced so incredibly easily. No one should have that much power over social interactions.
Will we on-board a massive wave of TikTokers in the coming hours or days? I don't know.
TikTokers may not be ready for Nostr yet, and honestly, Nostr may not be ready for them either. The ecosystem still lacks the completely polished applications, tools, and services they’re accustomed to. This is where we say "we're still early". They may not be early adopters like the current Nostr user base. Until we bridge that gap, they’ll likely move to the next centralized platform, only to face another government ban or round of censorship in the future. But eventually, there will come a tipping point, a moment when they’ve had enough. When that time comes, I hope we’re prepared. If we’re not, we risk missing a tremendous opportunity to onboard people who genuinely need Nostr’s freedom.
Until then, to all of the Nostr developers out there, keep up the great work and keep building. Your hard work and determination is needed.
-
 @ e5272de9:a16a102f
2024-09-08 19:21:40
@ e5272de9:a16a102f
2024-09-08 19:21:40The Grapevine is designed to digest raw data, no matter where you can find it. This is made possible through the process of interpretation.
Interpretation: the process of converting a source of raw data into a format suitable for consumption by the grapevine algorithm
format of Grapevine ratings
The Grapevine is designed to take as input a list of ratings that follow a specialized format, which we will refer to as Grapevine ratings.
Each rating must contain the following 4 to 6 fields: - rater - ratee - score - confidence - context (optional) - rating type (optional)
rater
The author of the rating. Often will be a pubkey or an npub, but could be username, etc.
ratee
The person, place, or thing being rated. This could be a pubkey, an event id or naddr, or a simple string, e.g. the title of a movie.
score
usually a number, but could be a boolean, an item on a list, etc.
confidence
a number between 0 and 1 (i.e. 0 and 100 percent) that represents the confidence of the rater in the score. For example: If Alice rates Bob as highly skilled in some context, and this is based on working with him for many years, she may rate him 9/10 with a confidence of 0.9 (90 percent). On the other hand, suppose she considers him worthy of a 9/10 rating, but this is based on only one brief interaction. In this case, she may rate him 9/10 but with a confidence of 0.05 (5 percent).
context
a string. This may be omitted from the table if every rating in the table or dataset is of the same context (as may often be the case).
rating type
a string that indicates the type of rating: 5 star, true or false, etc. This may be omitted from the table if every rating in the table or dataset is of the same rating type (as may often be the case).
Example interpretation: follows and mutes
A good way to bootstrap a list of nostr users minus the bots, scams, and other bad actors is to make use of the follows and mutes lists, as is done at brainstorm.
The interpretation of a follow is the following Grapevine Rating: - rater: pk_Alice - ratee: pk_Bob - score: 1 - confidence: 0.05
The interpretation of a mute is the following Grapevine Rating: - rater: pk_Alice - ratee: pk_Charlie - score: 0 - confidence: 0.1
Grapevine Ratings Tables
A list of ratings may be referred to as a Grapevine Ratings Table or a Grapevine Ratings Dataset (if in some non-table format, such as an object).
In the below example, the rating type (0 to 5 stars) and context (item quality) columns are the same for each row in the table and so are omitted.
| rater | ratee | score | confidence | | --- | --- | --- | --- | | pk_Alice | item1 | 4 | 0.5 | | pk_Bob | item1 | 5 | 0.9 | | pk_Alice | item2 | 0 | 0.1 |
Sources of Raw Data
| Some Suggested Sources of Raw Data | | --- | | follows, mutes, zaps | | kind 1 and long form notes | | NIP-51 lists | | kind 7 reactions | | NIP-32 labels | | NIP-58 badges | | nostr forms (e.g. see formstr) |
-
 @ cff1720e:15c7e2b2
2025-01-19 17:48:02
@ cff1720e:15c7e2b2
2025-01-19 17:48:02Einleitung\ \ Schwierige Dinge einfach zu erklären ist der Anspruch von ELI5 (explain me like I'm 5). Das ist in unserer hoch technisierten Welt dringend erforderlich, denn nur mit dem Verständnis der Technologien können wir sie richtig einsetzen und weiter entwickeln.\ Ich starte meine Serie mit Nostr, einem relativ neuen Internet-Protokoll. Was zum Teufel ist ein Internet-Protokoll? Formal beschrieben sind es internationale Standards, die dafür sorgen, dass das Internet seit über 30 Jahren ziemlich gut funktioniert. Es ist die Sprache, in der sich die Rechner miteinander unterhalten und die auch Sie täglich nutzen, vermutlich ohne es bewusst wahrzunehmen. http(s) transportiert ihre Anfrage an einen Server (z.B. Amazon), und html sorgt dafür, dass aus den gelieferten Daten eine schöne Seite auf ihrem Bildschirm entsteht. Eine Mail wird mit smtp an den Mailserver gesendet und mit imap von ihm abgerufen, und da alle den Standard verwenden, funktioniert das mit jeder App auf jedem Betriebssystem und mit jedem Mail-Provider. Und mit einer Mail-Adresse wie roland@pareto.space können sie sogar jederzeit umziehen, egal wohin. Cool, das ist state of the art! Aber warum funktioniert das z.B. bei Chat nicht, gibt es da kein Protokoll? Doch, es heißt IRC (Internet Relay Chat → merken sie sich den Namen), aber es wird so gut wie nicht verwendet. Die Gründe dafür sind nicht technischer Natur, vielmehr wurden mit Apps wie Facebook, Twitter, WhatsApp, Telegram, Instagram, TikTok u.a. bewusst Inkompatibilitäten und Nutzerabhängigkeiten geschaffen um Profite zu maximieren.

Warum Nostr?
Da das Standard-Protokoll nicht genutzt wird, hat jede App ihr eigenes, und wir brauchen eine handvoll Apps um uns mit allen Bekannten auszutauschen. Eine Mobilfunknummer ist Voraussetzung für jedes Konto, damit können die App-Hersteller die Nutzer umfassend tracken und mit dem Verkauf der Informationen bis zu 30 USD je Konto und Monat verdienen. Der Nutzer ist nicht mehr Kunde, er ist das Produkt! Der Werbe-SPAM ist noch das kleinste Problem bei diesem Geschäftsmodell. Server mit Millionen von Nutzerdaten sind ein “honey pot”, dementsprechend oft werden sie gehackt und die Zugangsdaten verkauft. 2024 wurde auch der Twitter-Account vom damaligen Präsidenten Joe Biden gehackt, niemand wusste mehr wer die Nachrichten verfasst hat (vorher auch nicht), d.h. die Authentizität der Inhalte ist bei keinem dieser Anbieter gewährleistet. Im selben Jahr wurde der Telegram-Gründer in Frankreich in Beugehaft genommen, weil er sich geweigert hatte Hintertüren in seine Software einzubauen. Nun kann zum Schutz "unserer Demokratie” praktisch jeder mitlesen, was sie mit wem an Informationen austauschen, z.B. darüber welches Shampoo bestimmte Politiker verwenden.

Und wer tatsächlich glaubt er könne Meinungsfreiheit auf sozialen Medien praktizieren, findet sich schnell in der Situation von Donald Trump wieder (seinerzeit amtierender Präsident), dem sein Twitter-Konto 2021 abgeschaltet wurde (Cancel-Culture). Die Nutzerdaten, also ihr Profil, ihre Kontakte, Dokumente, Bilder, Videos und Audiofiles - gehören ihnen ohnehin nicht mehr sondern sind Eigentum des Plattform-Betreibers; lesen sie sich mal die AGB's durch. Aber nein, keine gute Idee, das sind hunderte Seiten und sie werden permanent geändert. Alle nutzen also Apps, deren Technik sie nicht verstehen, deren Regeln sie nicht kennen, wo sie keine Rechte haben und die ihnen die Resultate ihres Handelns stehlen. Was würde wohl der Fünfjährige sagen, wenn ihm seine ältere Schwester anbieten würde, alle seine Spielzeuge zu “verwalten” und dann auszuhändigen wenn er brav ist? “Du spinnst wohl”, und damit beweist der Knirps mehr Vernunft als die Mehrzahl der Erwachsenen. \ \ Resümee: keine Standards, keine Daten, keine Rechte = keine Zukunft!

\ Wie funktioniert Nostr?
Die Entwickler von Nostr haben erkannt dass sich das Server-Client-Konzept in ein Master-Slave-Konzept verwandelt hatte. Der Master ist ein Synonym für Zentralisierung und wird zum “single point of failure”, der zwangsläufig Systeme dysfunktional macht. In einem verteilten Peer2Peer-System gibt es keine Master mehr sondern nur gleichberechtigte Knoten (Relays), auf denen die Informationen gespeichert werden. Indem man Informationen auf mehreren Relays redundant speichert, ist das System in jeglicher Hinsicht resilienter. Nicht nur die Natur verwendet dieses Prinzip seit Jahrmillionen erfolgreich, auch das Internet wurde so konzipiert (das ARPAnet wurde vom US-Militär für den Einsatz in Kriegsfällen unter massiven Störungen entwickelt). Alle Nostr-Daten liegen auf Relays und der Nutzer kann wählen zwischen öffentlichen (zumeist kostenlosen) und privaten Relays, z.B. für geschlossene Gruppen oder zum Zwecke von Daten-Archivierung. Da Dokumente auf mehreren Relays gespeichert sind, werden statt URL's (Locator) eindeutige Dokumentnamen (URI's = Identifier) verwendet, broken Links sind damit Vergangenheit und Löschungen / Verluste ebenfalls.\ \ Jedes Dokument (Event genannt) wird vom Besitzer signiert, es ist damit authentisch und fälschungssicher und kann nur vom Ersteller gelöscht werden. Dafür wird ein Schlüsselpaar verwendet bestehend aus privatem (nsec) und öffentlichem Schlüssel (npub) wie aus der Mailverschlüsselung (PGP) bekannt. Das repräsentiert eine Nostr-Identität, die um Bild, Namen, Bio und eine lesbare Nostr-Adresse ergänzt werden kann (z.B. roland@pareto.space ), mehr braucht es nicht um alle Ressourcen des Nostr-Ökosystems zu nutzen. Und das besteht inzwischen aus über hundert Apps mit unterschiedlichen Fokussierungen, z.B. für persönliche verschlüsselte Nachrichten (DM → OxChat), Kurznachrichten (Damus, Primal), Blogbeiträge (Pareto), Meetups (Joinstr), Gruppen (Groups), Bilder (Olas), Videos (Amethyst), Audio-Chat (Nostr Nests), Audio-Streams (Tunestr), Video-Streams (Zap.Stream), Marktplätze (Shopstr) u.v.a.m. Die Anmeldung erfolgt mit einem Klick (single sign on) und den Apps stehen ALLE Nutzerdaten zur Verfügung (Profil, Daten, Kontakte, Social Graph → Follower, Bookmarks, Comments, etc.), im Gegensatz zu den fragmentierten Datensilos der Gegenwart.\ \ Resümee: ein offener Standard, alle Daten, alle Rechte = große Zukunft!

\ Warum ist Nostr die Zukunft des Internet?
“Baue Dein Haus nicht auf einem fremden Grundstück” gilt auch im Internet - für alle App-Entwickler, Künstler, Journalisten und Nutzer, denn auch ihre Daten sind werthaltig. Nostr garantiert das Eigentum an den Daten, und überwindet ihre Fragmentierung. Weder die Nutzung noch die kreativen Freiheiten werden durch maßlose Lizenz- und Nutzungsbedingungen eingeschränkt. Aus passiven Nutzern werden durch Interaktion aktive Teilnehmer, Co-Creatoren in einer Sharing-Ökonomie (Value4Value). OpenSource schafft endlich wieder Vertrauen in die Software und ihre Anbieter. Offene Standards ermöglichen den Entwicklern mehr Kooperation und schnellere Entwicklung, für die Anwender garantieren sie Wahlfreiheit. Womit wir letztmalig zu unserem Fünfjährigen zurückkehren. Kinder lieben Lego über alles, am meisten die Maxi-Box “Classic”, weil sie damit ihre Phantasie im Kombinieren voll ausleben können. Erwachsene schenken ihnen dann die viel zu teuren Themenpakete, mit denen man nur eine Lösung nach Anleitung bauen kann. “Was stimmt nur mit meinen Eltern nicht, wann sind die denn falsch abgebogen?" fragt sich der Nachwuchs zu Recht. Das Image lässt sich aber wieder aufpolieren, wenn sie ihren Kindern Nostr zeigen, denn die Vorteile verstehen sogar Fünfjährige.

\ Das neue Internet ist dezentral. Das neue Internet ist selbstbestimmt. Nostr ist das neue Internet.
https://nostr.net/ \ https://start.njump.me/
Hier das Interview zum Thema mit Radio Berliner Morgenröte
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28A Causa
o Princípios de Economia Política de Menger é o único livro que enfatiza a CAUSA o tempo todo. os cientistas todos parecem não saber, ou se esquecer sempre, que as coisas têm causa, e que o conhecimento verdadeiro é o conhecimento da causa das coisas.
a causa é uma categoria metafísica muito superior a qualquer correlação ou resultado de teste de hipótese, ela não pode ser descoberta por nenhum artifício econométrico ou reduzida à simples antecedência temporal estatística. a causa dos fenômenos não pode ser provada cientificamente, mas pode ser conhecida.
o livro de Menger conta para o leitor as causas de vários fenômenos econômicos e as interliga de forma que o mundo caótico da economia parece adquirir uma ordem no momento em que você lê. é uma sensação mágica e indescritível.
quando eu te o recomendei, queria é te imbuir com o espírito da busca pela causa das coisas. depois de ler aquilo, você está apto a perceber continuidade causal nos fenômenos mais complexos da economia atual, enxergar as causas entre toda a ação governamental e as suas várias consequências na vida humana. eu faço isso todos os dias e é a melhor sensação do mundo quando o caos das notícias do caderno de Economia do jornal -- que para o próprio jornalista que as escreveu não têm nenhum sentido (tanto é que ele escreve tudo errado) -- se incluem num sistema ordenado de causas e consequências.
provavelmente eu sempre erro em alguns ou vários pontos, mas ainda assim é maravilhoso. ou então é mais maravilhoso ainda quando eu descubro o erro e reinsiro o acerto naquela racionalização bela da ordem do mundo econômico que é a ordem de Deus.
em scrap para T.P.
-
 @ 472f440f:5669301e
2024-09-06 21:56:48
@ 472f440f:5669301e
2024-09-06 21:56:48I had the pleasure of sitting back down with Will Reeves, Founder and CEO of Fold, on TFTC last week to discuss Fold's journey from a startup to (soon to be) a publicly listed company. I particularly liked this conversation because it was a great lens into the grit it takes to run a successful bitcoin company.
https://fountain.fm/episode/1FrspxmpK5bsoReGx73n
Building a successful company is extremely hard in its own right. Building a successful bitcoin company is significantly harder considering the fact that you're building a company in parallel with a nascent and volatile monetary asset that is monetizing in real time. Bitcoin adoption comes in waves. People flood in when the price is ripping and fade out when the price corrects and goes into a multi-year bear market before the tide comes back in. This means that your potential user base is expanding and contracting more than it would be in other industries. As a company you need to be able to absorb the incoming waves of new adopters and then capture and retain the users who stick around for the bear market.
To do this correctly, a founder and their team needs to thread many needles. First, can you assemble a team that can actually build something? Second, can you bring a product to market that people actually use because it provides value to them? Third, can you stick out against the crowd? So on and so forth. One of the most important aspects of building a bitcoin company during bitcoin's monetization phase is timing. There are many great ideas that people have in terms of companies, products and tools that can built using bitcoin. There are sci-fi futures that can be built today on bitcoin if people really wanted to.
The problem that arises is that adoption and understanding of bitcoin are at a point where, even though a functional product could be brought to market, it won't be adopted by a large number of people because there 1.) aren't enough people who would understand how to use it and 2.) for the people who do understand how to use it and could benefit from it, the universe of people they can interact with using that product is minuscule.
Timing is everything. And I think Fold nailed the timing of their product. Allowing people to passively stack sats by offering a product that enables them to go about their daily spending and get sats back instead of cash back rewards is a great first-touch bitcoin experience. Once Fold found their sticky user base and perfected their sats back experience, they began expanding their product offering to provide their users with more bitcoin services. Buy/sell bitcoin in-app, bill pay for sats back, and more. They'll eventually roll out a credit card and additional financial services. Start simple, provide something of value, nail the timing and then expand from there. That seems to be the recipe.
For any founders in the space reading this, I highly recommend you listen to the episode. Particularly for the advice Will gives about knowing when to sprint on product and when to lean into growth. Bear markets are for building and bull markets are for casting the widest net possible and capturing as many new users as possible.
At Ten31 we are extremely proud to back Fold and a number of other companies in the bitcoin space that understand the intricacies described above. We work with some of the best founders in the world. Founders who know how to eat glass with the best of them. Bitcoin can be a cruel mistress and no one knows that more intimately than the founders building bitcoin companies.
Final thought...
The NFL having a week 1 game in Brazil should get Roger Godell fired.
Enjoy your weekend, freaks.
-
 @ e3ba5e1a:5e433365
2025-02-04 08:29:00
@ e3ba5e1a:5e433365
2025-02-04 08:29:00President Trump has started rolling out his tariffs, something I blogged about in November. People are talking about these tariffs a lot right now, with many people (correctly) commenting on how consumers will end up with higher prices as a result of these tariffs. While that part is true, I’ve seen a lot of people taking it to the next, incorrect step: that consumers will pay the entirety of the tax. I put up a poll on X to see what people thought, and while the right answer got a lot of votes, it wasn't the winner.

For purposes of this blog post, our ultimate question will be the following:
- Suppose apples currently sell for $1 each in the entire United States.
- There are domestic sellers and foreign sellers of apples, all receiving the same price.
- There are no taxes or tariffs on the purchase of apples.
- The question is: if the US federal government puts a $0.50 import tariff per apple, what will be the change in the following:
- Number of apples bought in the US
- Price paid by buyers for apples in the US
- Post-tax price received by domestic apple producers
- Post-tax price received by foreign apple producers
Before we can answer that question, we need to ask an easier, first question: before instituting the tariff, why do apples cost $1?
And finally, before we dive into the details, let me provide you with the answers to the ultimate question. I recommend you try to guess these answers before reading this, and if you get it wrong, try to understand why:
- The number of apples bought will go down
- The buyers will pay more for each apple they buy, but not the full amount of the tariff
- Domestic apple sellers will receive a higher price per apple
- Foreign apple sellers will receive a lower price per apple, but not lowered by the full amount of the tariff
In other words, regardless of who sends the payment to the government, both taxed parties (domestic buyers and foreign sellers) will absorb some of the costs of the tariff, while domestic sellers will benefit from the protectionism provided by tariffs and be able to sell at a higher price per unit.
Marginal benefit
All of the numbers discussed below are part of a helper Google Sheet I put together for this analysis. Also, apologies about the jagged lines in the charts below, I hadn’t realized before starting on this that there are some difficulties with creating supply and demand charts in Google Sheets.
Let’s say I absolutely love apples, they’re my favorite food. How much would I be willing to pay for a single apple? You might say “$1, that’s the price in the supermarket,” and in many ways you’d be right. If I walk into supermarket A, see apples on sale for $50, and know that I can buy them at supermarket B for $1, I’ll almost certainly leave A and go buy at B.
But that’s not what I mean. What I mean is: how high would the price of apples have to go everywhere so that I’d no longer be willing to buy a single apple? This is a purely personal, subjective opinion. It’s impacted by how much money I have available, other expenses I need to cover, and how much I like apples. But let’s say the number is $5.
How much would I be willing to pay for another apple? Maybe another $5. But how much am I willing to pay for the 1,000th apple? 10,000th? At some point, I’ll get sick of apples, or run out of space to keep the apples, or not be able to eat, cook, and otherwise preserve all those apples before they rot.
The point being: I’ll be progressively willing to spend less and less money for each apple. This form of analysis is called marginal benefit: how much benefit (expressed as dollars I’m willing to spend) will I receive from each apple? This is a downward sloping function: for each additional apple I buy (quantity demanded), the price I’m willing to pay goes down. This is what gives my personal demand curve. And if we aggregate demand curves across all market participants (meaning: everyone interested in buying apples), we end up with something like this:
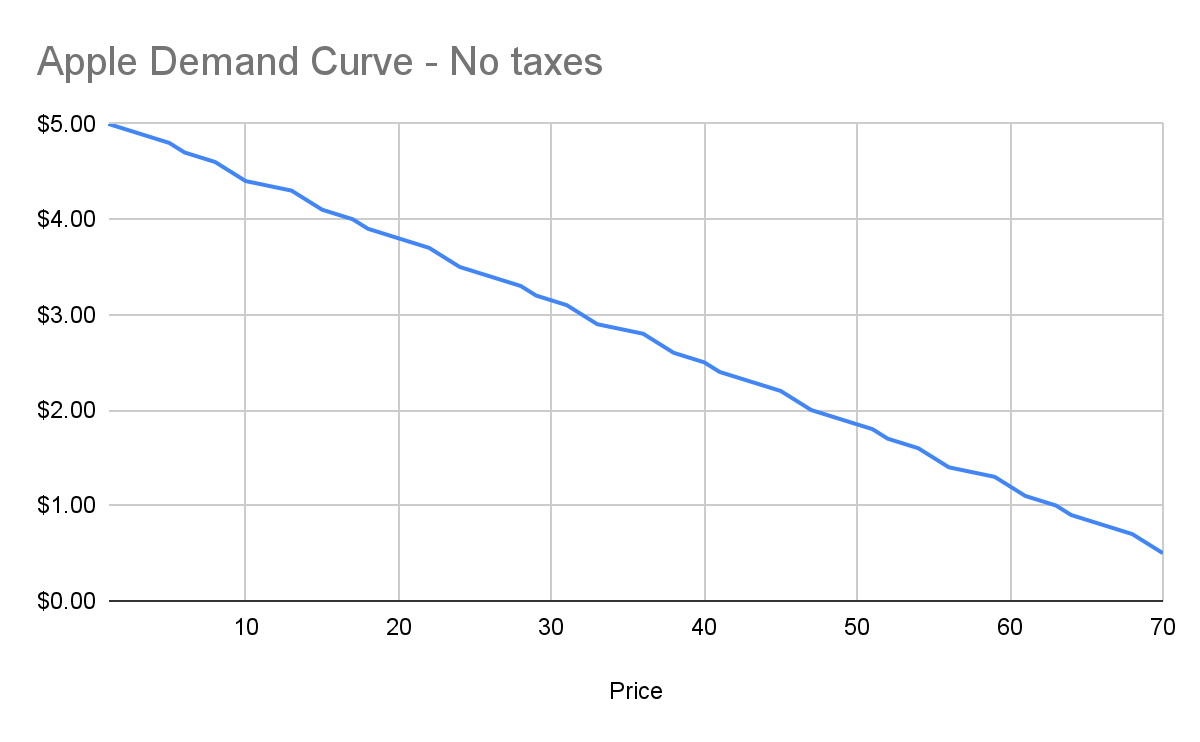
Assuming no changes in people’s behavior and other conditions in the market, this chart tells us how many apples will be purchased by our buyers at each price point between $0.50 and $5. And ceteris paribus (all else being equal), this will continue to be the demand curve for apples.
Marginal cost
Demand is half the story of economics. The other half is supply, or: how many apples will I sell at each price point? Supply curves are upward sloping: the higher the price, the more a person or company is willing and able to sell a product.
Let’s understand why. Suppose I have an apple orchard. It’s a large property right next to my house. With about 2 minutes of effort, I can walk out of my house, find the nearest tree, pick 5 apples off the tree, and call it a day. 5 apples for 2 minutes of effort is pretty good, right?
Yes, there was all the effort necessary to buy the land, and plant the trees, and water them… and a bunch more than I likely can’t even guess at. We’re going to ignore all of that for our analysis, because for short-term supply-and-demand movement, we can ignore these kinds of sunk costs. One other simplification: in reality, supply curves often start descending before ascending. This accounts for achieving efficiencies of scale after the first number of units purchased. But since both these topics are unneeded for understanding taxes, I won’t go any further.
Anyway, back to my apple orchard. If someone offers me $0.50 per apple, I can do 2 minutes of effort and get $2.50 in revenue, which equates to a $75/hour wage for me. I’m more than happy to pick apples at that price!
However, let’s say someone comes to buy 10,000 apples from me instead. I no longer just walk out to my nearest tree. I’m going to need to get in my truck, drive around, spend the day in the sun, pay for gas, take a day off of my day job (let’s say it pays me $70/hour). The costs go up significantly. Let’s say it takes 5 days to harvest all those apples myself, it costs me $100 in fuel and other expenses, and I lose out on my $70/hour job for 5 days. We end up with:
- Total expenditure: $100 + $70 * 8 hours a day * 5 days \== $2900
- Total revenue: $5000 (10,000 apples at $0.50 each)
- Total profit: $2100
So I’m still willing to sell the apples at this price, but it’s not as attractive as before. And as the number of apples purchased goes up, my costs keep increasing. I’ll need to spend more money on fuel to travel more of my property. At some point I won’t be able to do the work myself anymore, so I’ll need to pay others to work on the farm, and they’ll be slower at picking apples than me (less familiar with the property, less direct motivation, etc.). The point being: at some point, the number of apples can go high enough that the $0.50 price point no longer makes me any money.
This kind of analysis is called marginal cost. It refers to the additional amount of expenditure a seller has to spend in order to produce each additional unit of the good. Marginal costs go up as quantity sold goes up. And like demand curves, if you aggregate this data across all sellers, you get a supply curve like this:
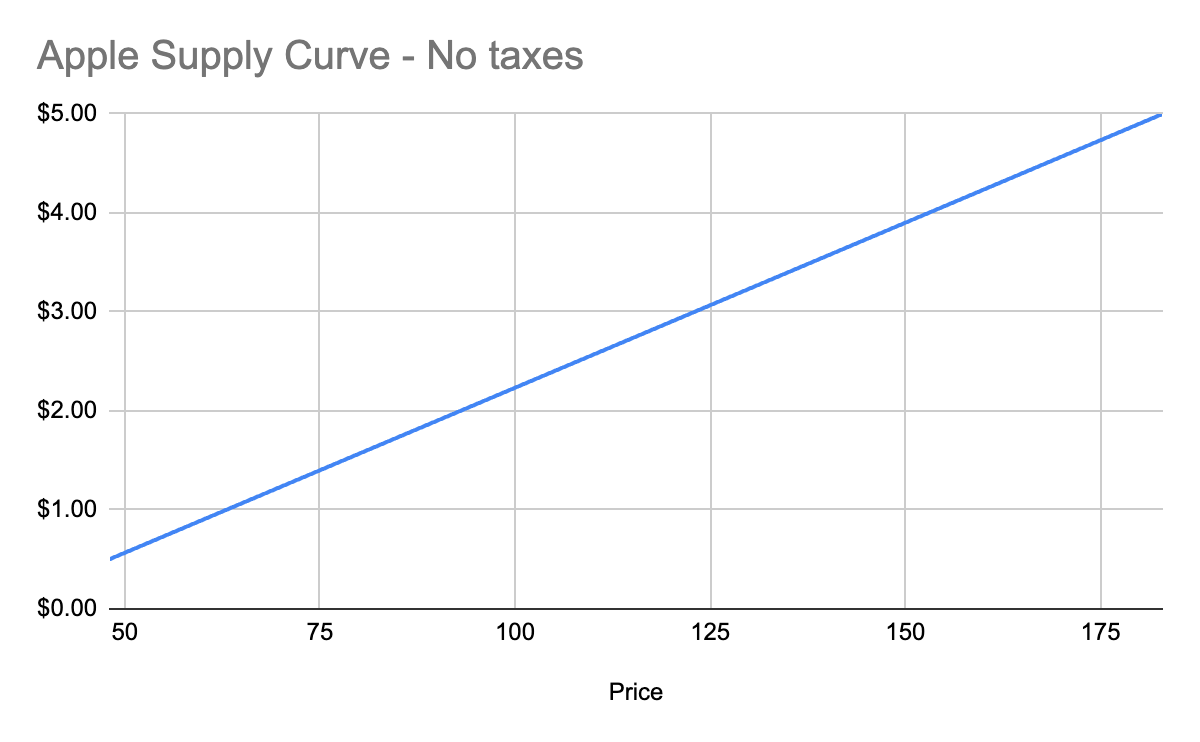
Equilibrium price
We now know, for every price point, how many apples buyers will purchase, and how many apples sellers will sell. Now we find the equilibrium: where the supply and demand curves meet. This point represents where the marginal benefit a buyer would receive from the next buyer would be less than the cost it would take the next seller to make it. Let’s see it in a chart:
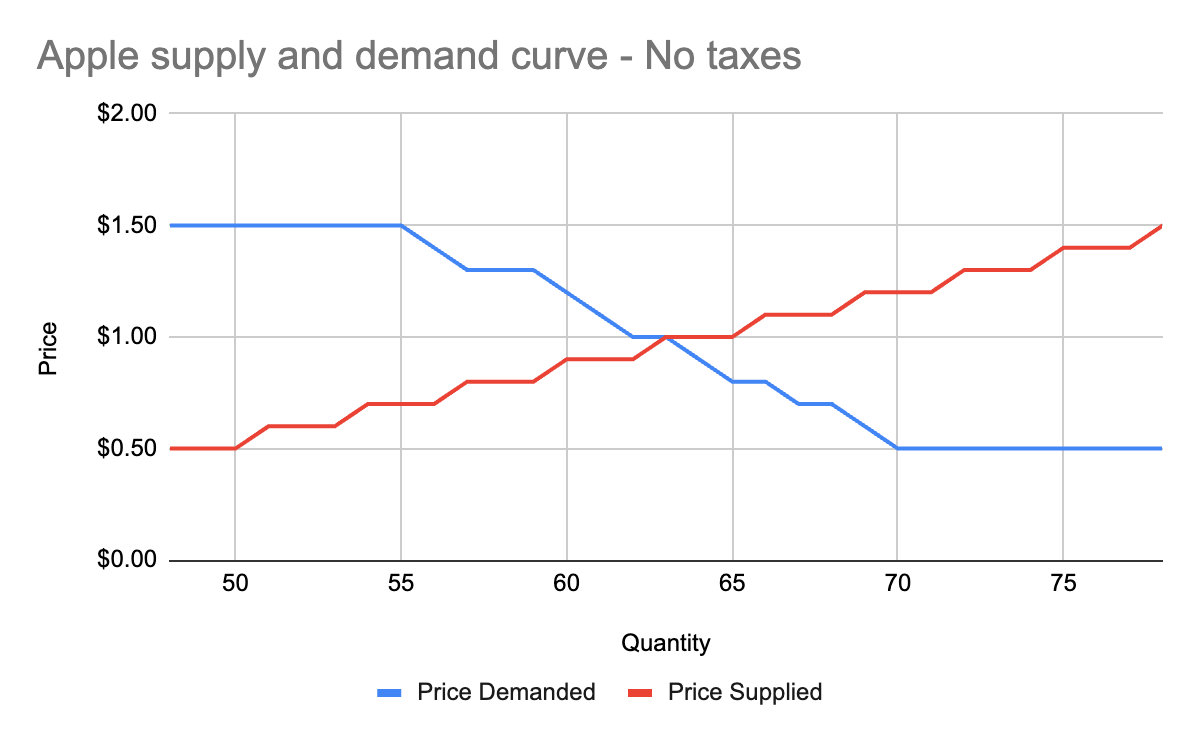
You’ll notice that these two graphs cross at the $1 price point, where 63 apples are both demanded (bought by consumers) and supplied (sold by producers). This is our equilibrium price. We also have a visualization of the surplus created by these trades. Everything to the left of the equilibrium point and between the supply and demand curves represents surplus: an area where someone is receiving something of more value than they give. For example:
- When I bought my first apple for $1, but I was willing to spend $5, I made $4 of consumer surplus. The consumer portion of the surplus is everything to the left of the equilibrium point, between the supply and demand curves, and above the equilibrium price point.
- When a seller sells his first apple for $1, but it only cost $0.50 to produce it, the seller made $0.50 of producer surplus. The producer portion of the surplus is everything to the left of the equilibrium point, between the supply and demand curves, and below the equilibrium price point.
Another way of thinking of surplus is “every time someone got a better price than they would have been willing to take.”
OK, with this in place, we now have enough information to figure out how to price in the tariff, which we’ll treat as a negative externality.
Modeling taxes
Alright, the government has now instituted a $0.50 tariff on every apple sold within the US by a foreign producer. We can generally model taxes by either increasing the marginal cost of each unit sold (shifting the supply curve up), or by decreasing the marginal benefit of each unit bought (shifting the demand curve down). In this case, since only some of the producers will pay the tax, it makes more sense to modify the supply curve.
First, let’s see what happens to the foreign seller-only supply curve when you add in the tariff:
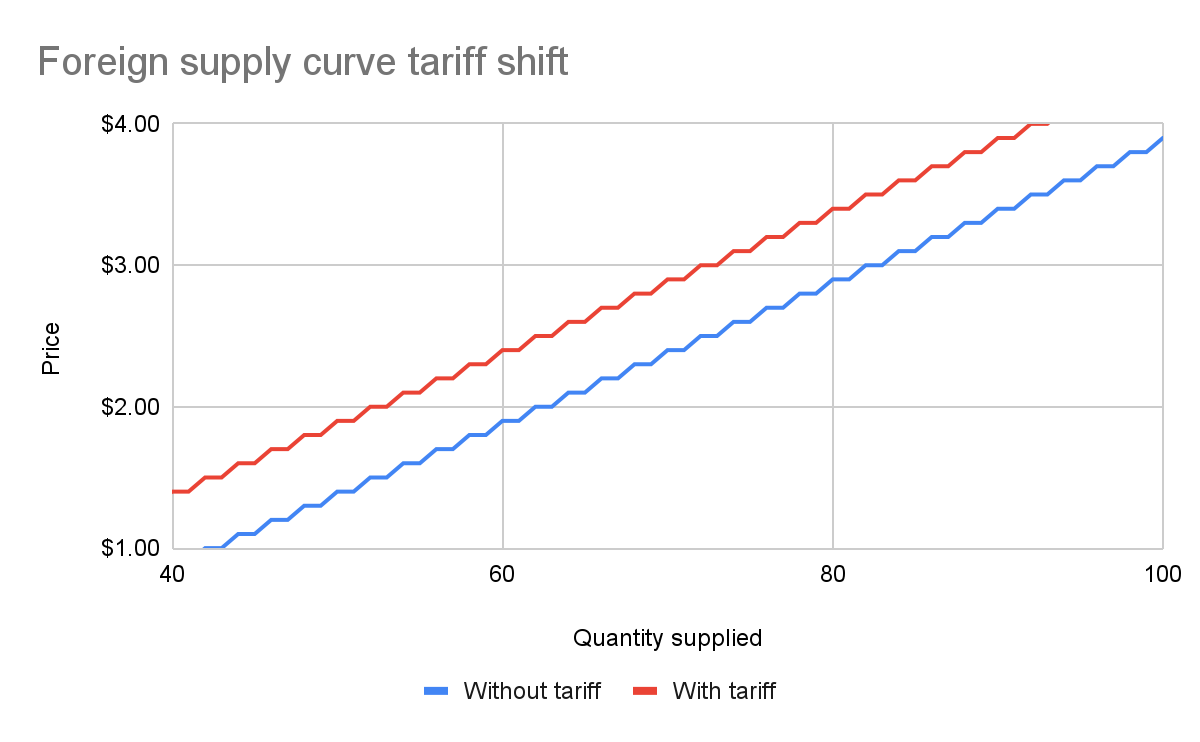
With the tariff in place, for each quantity level, the price at which the seller will sell is $0.50 higher than before the tariff. That makes sense: if I was previously willing to sell my 82nd apple for $3, I would now need to charge $3.50 for that apple to cover the cost of the tariff. We see this as the tariff “pushing up” or “pushing left” the original supply curve.
We can add this new supply curve to our existing (unchanged) supply curve for domestic-only sellers, and we end up with a result like this:
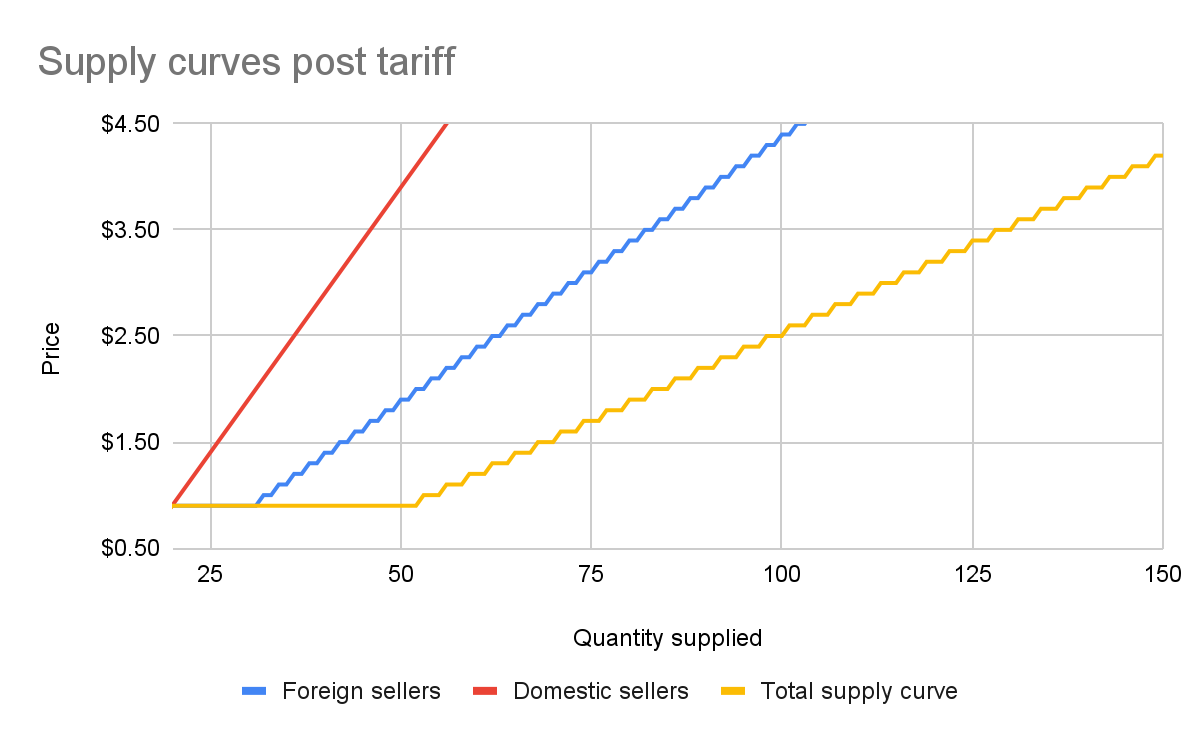
The total supply curve adds up the individual foreign and domestic supply curves. At each price point, we add up the total quantity each group would be willing to sell to determine the total quantity supplied for each price point. Once we have that cumulative supply curve defined, we can produce an updated supply-and-demand chart including the tariff:
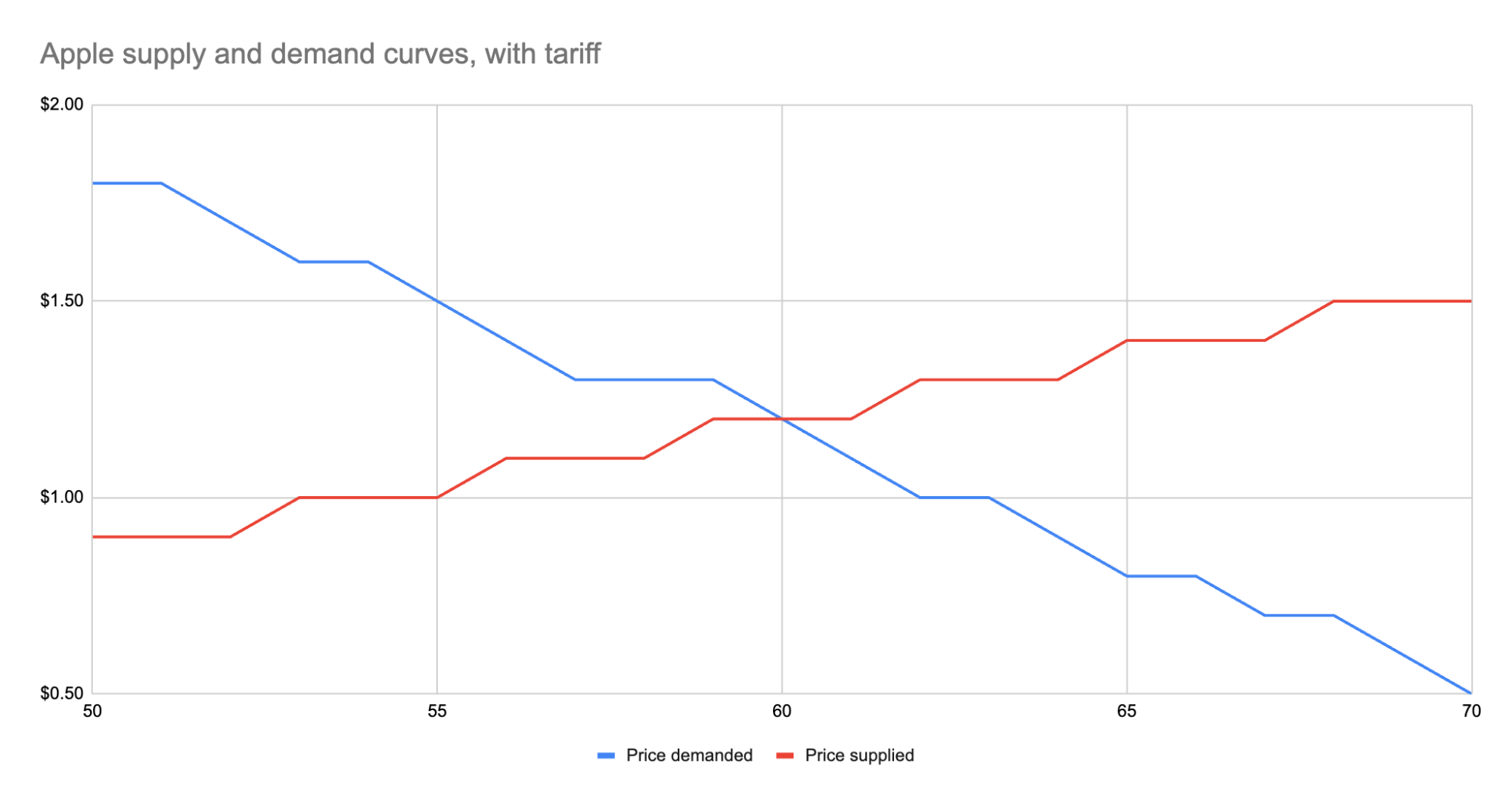
As we can see, the equilibrium has shifted:
- The equilibrium price paid by consumers has risen from $1 to $1.20.
- The total number of apples purchased has dropped from 63 apples to 60 apples.
- Consumers therefore received 3 less apples. They spent $72 for these 60 apples, whereas previously they spent $63 for 3 more apples, a definite decrease in consumer surplus.
- Foreign producers sold 36 of those apples (see the raw data in the linked Google Sheet), for a gross revenue of $43.20. However, they also need to pay the tariff to the US government, which accounts for $18, meaning they only receive $25.20 post-tariff. Previously, they sold 42 apples at $1 each with no tariff to be paid, meaning they took home $42.
- Domestic producers sold the remaining 24 apples at $1.20, giving them a revenue of $28.80. Since they don’t pay the tariff, they take home all of that money. By contrast, previously, they sold 21 apples at $1, for a take-home of $21.
- The government receives $0.50 for each of the 60 apples sold, or in other words receives $30 in revenue it wouldn’t have received otherwise.
We could be more specific about the surpluses, and calculate the actual areas for consumer surplus, producer surplus, inefficiency from the tariff, and government revenue from the tariff. But I won’t bother, as those calculations get slightly more involved. Instead, let’s just look at the aggregate outcomes:
- Consumers were unquestionably hurt. Their price paid went up by $0.20 per apple, and received less apples.
- Foreign producers were also hurt. Their price received went down from the original $1 to the new post-tariff price of $1.20, minus the $0.50 tariff. In other words: foreign producers only receive $0.70 per apple now. This hurt can be mitigated by shifting sales to other countries without a tariff, but the pain will exist regardless.
- Domestic producers scored. They can sell less apples and make more revenue doing it.
- And the government walked away with an extra $30.
Hopefully you now see the answer to the original questions. Importantly, while the government imposed a $0.50 tariff, neither side fully absorbed that cost. Consumers paid a bit more, foreign producers received a bit less. The exact details of how that tariff was split across the groups is mediated by the relevant supply and demand curves of each group. If you want to learn more about this, the relevant search term is “price elasticity,” or how much a group’s quantity supplied or demanded will change based on changes in the price.
Other taxes
Most taxes are some kind of a tax on trade. Tariffs on apples is an obvious one. But the same applies to income tax (taxing the worker for the trade of labor for money) or payroll tax (same thing, just taxing the employer instead). Interestingly, you can use the same model for analyzing things like tax incentives. For example, if the government decided to subsidize domestic apple production by giving the domestic producers a $0.50 bonus for each apple they sell, we would end up with a similar kind of analysis, except instead of the foreign supply curve shifting up, we’d see the domestic supply curve shifting down.
And generally speaking, this is what you’ll always see with government involvement in the economy. It will result in disrupting an existing equilibrium, letting the market readjust to a new equilibrium, and incentivization of some behavior, causing some people to benefit and others to lose out. We saw with the apple tariff, domestic producers and the government benefited while others lost.
You can see the reverse though with tax incentives. If I give a tax incentive of providing a deduction (not paying income tax) for preschool, we would end up with:
- Government needs to make up the difference in tax revenue, either by raising taxes on others or printing more money (leading to inflation). Either way, those paying the tax or those holding government debased currency will pay a price.
- Those people who don’t use the preschool deduction will receive no benefit, so they simply pay a cost.
- Those who do use the preschool deduction will end up paying less on tax+preschool than they would have otherwise.
This analysis is fully amoral. It’s not saying whether providing subsidized preschool is a good thing or not, it simply tells you where the costs will be felt, and points out that such government interference in free economic choice does result in inefficiencies in the system. Once you have that knowledge, you’re more well educated on making a decision about whether the costs of government intervention are worth the benefits.
-
 @ 6389be64:ef439d32
2025-01-16 15:44:06
@ 6389be64:ef439d32
2025-01-16 15:44:06Black Locust can grow up to 170 ft tall
Grows 3-4 ft. per year
Native to North America
Cold hardy in zones 3 to 8

Firewood
- BLT wood, on a pound for pound basis is roughly half that of Anthracite Coal
- Since its growth is fast, firewood can be plentiful
Timber

- Rot resistant due to a naturally produced robinin in the wood
- 100 year life span in full soil contact! (better than cedar performance)
- Fence posts
- Outdoor furniture
- Outdoor decking
- Sustainable due to its fast growth and spread
- Can be coppiced (cut to the ground)
- Can be pollarded (cut above ground)
- Its dense wood makes durable tool handles, boxes (tool), and furniture
- The wood is tougher than hickory, which is tougher than hard maple, which is tougher than oak.
- A very low rate of expansion and contraction
- Hardwood flooring
- The highest tensile beam strength of any American tree
- The wood is beautiful
Legume
- Nitrogen fixer
- Fixes the same amount of nitrogen per acre as is needed for 200-bushel/acre corn
- Black walnuts inter-planted with locust as “nurse” trees were shown to rapidly increase their growth [[Clark, Paul M., and Robert D. Williams. (1978) Black walnut growth increased when interplanted with nitrogen-fixing shrubs and trees. Proceedings of the Indiana Academy of Science, vol. 88, pp. 88-91.]]
Bees

- The edible flower clusters are also a top food source for honey bees
Shade Provider

- Its light, airy overstory provides dappled shade
- Planted on the west side of a garden it provides relief during the hottest part of the day
- (nitrogen provider)
- Planted on the west side of a house, its quick growth soon shades that side from the sun
Wind-break

- Fast growth plus it's feathery foliage reduces wind for animals, crops, and shelters
Fodder
- Over 20% crude protein
- 4.1 kcal/g of energy
- Baertsche, S.R, M.T. Yokoyama, and J.W. Hanover (1986) Short rotation, hardwood tree biomass as potential ruminant feed-chemical composition, nylon bag ruminal degradation and ensilement of selected species. J. Animal Sci. 63 2028-2043
-
 @ 78c90fc4:4bff983c
2025-02-10 12:08:13
@ 78c90fc4:4bff983c
2025-02-10 12:08:13“Die Welt wird von ganz anderen Personen regiert als diejenigen es sich vorstellen, die nicht hinter den Kulissen stehen.”
Benjamin Disraeli, zweimaliger britischer Premierminister und Romanautor.
Quelle:
https://www.unz.com/article/the-disraeli-enigma/\ \ Als 1853 der Krimkrieg zwischen Russland und dem Osmanischen Reich ausbrach, wurde das Osmanische Reich vom Vereinigten Königreich und Frankreich gerettet. Zwanzig Jahre später zog Zar Alexander II. als Beschützer der unterdrückten serbischen und bulgarischen Christen erneut gegen die Osmanen in den Krieg. Als die Russen vor den Toren Konstantinopels/Istanbuls standen, waren die Osmanen gezwungen, die Schaffung der autonomen Fürstentümer Bulgarien, Serbien und Rumänien durch den Vertrag von San Stefano zu akzeptieren. Die Briten waren mit diesem Vertrag unzufrieden und beriefen zusammen mit Österreich-Ungarn den Berliner Kongress (1878) ein, der ihn aufhob. Russische Eroberungen wurden zurückgenommen, Armenien und Bulgarien wurden größtenteils an das Osmanische Reich zurückgegeben und der Balkan wurde in heterogene und konfliktreiche Staaten aufgeteilt. Diese „Balkanisierung“ löste nationalistische Ressentiments aus, die den Ersten Weltkrieg auslösen sollten.
\ Das Hauptziel des Berliner Vertrags bestand darin, das zu retten, was von einem schwächelnden Osmanischen Reich zu retten war, um der panslawistischen Expansion Russlands entgegenzuwirken. England, das stets eifersüchtig auf seine Vormachtstellung zur See bedacht war, wollte verhindern, dass Russland näher an den Bosporus heranrückte. Die Briten erhielten das Recht, Zypern als Marinestützpunkt zu nutzen und gleichzeitig den Suezkanal zu überwachen. Dies war der Beginn des „Great Game“ Großbritanniens um die Kolonialherrschaft in Asien und die Eindämmung Russlands, was insbesondere zur Schaffung Afghanistans als Pufferstaat führte.
\ Es gibt verschiedene Möglichkeiten, diesen Abschnitt der Geschichte zu interpretieren, der den Keim für alle Tragödien des 20. Jahrhunderts („das jüdische Jahrhundert“ laut Yuri Slezkine) in sich trägt.[1]\ Yuri Slezkine, The Jewish Century, Princeton University Press, 2004.
\ Es gibt unterschiedliche Ansichten darüber, welche Kräfte die Geschichte in dieser entscheidenden Zeit geprägt haben. Aber letztendlich wird Geschichte von Menschen gemacht, und sie kann nur verstanden werden, wenn man die Hauptakteure und ihre Motive identifiziert: Man kann den Vietnamkrieg einfach nicht verstehen, ohne sich mit der Denkweise von Johnson oder Kissinger auseinanderzusetzen. Unter den Anstiftern des Berliner Vertrags sticht ein Name besonders hervor: Benjamin Disraeli (1804–1881), Premierminister unter Königin Victoria von 1868 bis 1869 und erneut von 1874 bis 1880. Disraeli war auch der Mann, der 1875 die Übernahme des Suezkanals durch England ermöglichte, und zwar durch die Finanzierung seines Freundes Lionel de Rothschild, dem Sohn von Nathan Mayer – eine Operation, die die Kontrolle der Rothschilds über die Bank of England festigte.
\ Disraeli ist ein sehr interessanter Fall, da er sowohl ein bedeutender britischer Staatsmann während der globalen Hegemonie Großbritanniens als auch ein Romanautor war, der seine fiktiven Figuren dazu benutzte, seine ehrlichen Gedanken zu äußern, während er eine Art „glaubhafte Abstreitbarkeit“ (Sidonia spricht, nicht ich!) aufrechterhielt. Wir haben daher die einzigartige Gelegenheit, die wahren Motive des Mannes in der Politik zwischen den Zeilen zu lesen. Stellen Sie sich vor, Kissinger hätte Romane geschrieben, in denen ein Jude die Hauptfigur ist, der die Außen- und Militärpolitik des Imperiums vorantrieb und gleichzeitig ein enger Freund des reichsten jüdischen Bankiers war.\ \
Disraeli wird als der wahre Erfinder des Britischen Empires bezeichnet, da er es war, der Königin Victoria durch das Parlament mit dem Royal Titles Act von 1876 zur Kaiserin von Indien ernennen ließ (das obere Bild ist eine Karikatur, die Disraeli als Hausierer zeigt, der der Königin die Kaiserkrone überreicht).
Disraeli war, wie bereits erwähnt, die Hauptinspiration für den Berliner Kongress. Darüber hinaus war Disraeli ein Vorläufer des Zionismus, der versuchte, die „Wiederherstellung Israels“ auf die Tagesordnung des Berliner Kongresses zu setzen, in der Hoffnung, den Sultan Abdul Hamid davon zu überzeugen, Palästina als autonome Provinz zu gewähren. Der Sultan lehnte das Angebot ab, das wahrscheinlich das Versprechen finanzieller Unterstützung für seine zusammenbrechende Wirtschaft beinhaltete – wie auch Herzls Angebot im Jahr 1902, das ebenfalls abgelehnt wurde.\ \ Der Zionismus war Disraelis uralter Traum: Nach einer Reise in den Nahen Osten im Alter von sechsundzwanzig Jahren veröffentlichte er seinen ersten Roman, Die wundersame Geschichte des Alroy, und ließ seinen Helden, einen einflussreichen Juden des Mittelalters, sagen: „Mein Wunsch ist eine nationale Existenz, die wir nicht haben. Mein Wunsch ist das Land der Verheißung und Jerusalem und der Tempel, alles, was wir eingebüßt haben, wonach wir uns gesehnt haben, wofür wir gekämpft haben, unser schönes Land, unser heiliges Glaubensbekenntnis, unsere einfachen Sitten und unsere alten Bräuche.“\ Disraeli schrieb diese Zeilen noch vor den Anfängen der biblischen Archäologie; erst 1841 veröffentlichte Edward Robinson seine Biblical Researches in Palestine. Die ersten Ausgrabungen des von Königin Victoria geförderten Palestine Exploration Fund begannen 1867. Wohlhabende britische Juden hatten sich jedoch schon lange zuvor für Palästina interessiert. Disraelis Interesse wurde durch seinen Nachbarn und vierzigjährigen Freund Moses Montefiore beeinflusst, der Judith Cohen, die Schwägerin von Nathan Rothschild, heiratete. Nach einer Reise nach Palästina im Jahr 1827 widmete Montefiore seine immensen Ressourcen der Unterstützung seiner Glaubensgenossen im Heiligen Land, indem er Land kaufte und Häuser baute.
\ Sowohl Montefiore als auch Disraeli waren sephardischer Herkunft. Disraeli stammte aus einer Familie portugiesischer Marranen, die in Venedig zum Judentum konvertierten. Sein Großvater war 1748 nach London gezogen. Benjamin wurde im Alter von dreizehn Jahren getauft, als sein Vater Isaac D'Israeli zusammen mit seiner ganzen Familie zum anglikanischen Christentum konvertierte. Isaac D'Israeli ist der Autor eines Buches mit dem Titel The Genius of Judaism(in Anlehnung an Chateaubriands Le Génie du Christianisme), in dem er die einzigartigen Eigenschaften des jüdischen Volkes verherrlicht, aber die talmudischen Rabbiner dafür verantwortlich macht, dass sie „den nationalen Geist ihres Volkes versiegeln“ und „die Einfachheit ihres antiken Glaubens korrumpieren“. Wie für viele andere Juden dieser Zeit war die Konversion für D'Israeli rein opportunistisch: Bis zum Beginn des 19. Jahrhunderts blieben Verwaltungskarrieren für Juden verschlossen. Ein Gesetz von 1740 hatte ihre Einbürgerung erlaubt, aber es hatte Volksaufstände provoziert und wurde 1753 aufgehoben. Viele einflussreiche Juden, wie der Stadtbankier Sampson Gideon, entschieden sich dann für eine nominelle Konversion ihrer Kinder.[2]\ Cecil Roth, A History of the Marranos (1932), Meridian Books, 1959, S. 148.\ \ Etwa zur gleichen Zeit wie Disraeli konvertierte Heinrich Heine (1797–1856) zum Luthertum (während einer seiner Brüder zum Katholizismus konvertierte, um Offizier in Österreich zu werden, und ein anderer zur Orthodoxie, um als Arzt in Russland zu dienen). Heine betrachtete die Taufe als „Eintrittskarte in die europäische Zivilisation“. Er beklagte sich jedoch darüber, dass er von den Deutschen immer noch als Jude angesehen wurde, und zog es daher vor, in Frankreich zu leben, wo er als Deutscher angesehen wurde. Nur wenige Jahre nach seiner Konversion zeigten seine Schriften eine sehr negative Einstellung gegenüber dem Christentum, das er als „düstere, blutrünstige Religion für Kriminelle“ bezeichnete, die die Sinnlichkeit unterdrücke. Am Ende seines Lebens bereute er seine Taufe, die ihm nichts gebracht hatte, und erklärte in seinem letzten Buch Romanzero: „Ich mache kein Geheimnis aus meinem Judentum, zu dem ich nicht zurückgekehrt bin, weil ich es nicht verlassen habe.“[3]\ Zitiert in Kevin MacDonald, Separation and Its Discontents: Toward an Evolutionary Theory of Anti-Semitism, Praeger, 1998, kindle 2013, l. 4732–4877.
\ Genau wie bei den portugiesischen Marranen im 15. Jahrhundert verstärkte die Taufe bei den europäischen Juden des 19. Jahrhunderts ein nicht-religiöses, rassisches Verständnis des Judentums. Disraeli bezeichnete sich selbst als „Anglikaner jüdischer Abstammung“.
\ Für Hannah Arendt ist Disraeli ein „Rassenfanatiker“, der in seinem ersten Roman Alroy (1833) „einen Plan für ein jüdisches Reich entwickelte, in dem Juden als streng getrennte Klasse herrschen würden“. In seinem anderen Roman Coningsby „entfaltete er einen fantastischen Plan, nach dem jüdisches Geld den Aufstieg und Fall von Höfen und Reichen beherrscht und in der Diplomatie die Oberhand hat“. Diese Idee „wurde zum Dreh- und Angelpunkt seiner politischen Philosophie“.[4]\ Hannah Arendt, The Origins of Totalitarianism, Band 1: Antisemitism, Meridian Books, 1958, S. 309–310.\ Dies ist eine ziemlich fantastische Anschuldigung, die die meisten Biografen Disraelis nicht bestätigen würden. Sie ist jedoch wahrscheinlich richtig. Aber wir müssen genau auf Disraelis eigene Stimme hören, die durch Sidonia zum Ausdruck kommt, die Figur, die in drei seiner Romane vorkommt: Coningsby (1844), Sybil (1845) und Tancred (1847).
In Sidonias Worten spürt man den Groll gegen die Nation, in die er sich zu integrieren versuchte:\ Kann es etwas Absurderes geben, als dass eine Nation sich an eine Einzelperson wendet, um ihren Kredit, ihre Existenz als Imperium und ihren Komfort als Volk zu erhalten; und diese Einzelperson, der ihre Gesetze die stolzesten Rechte der Staatsbürgerschaft, das Privileg, in ihrem Senat zu sitzen und Land zu besitzen, verweigern; denn obwohl ich unbesonnen genug war, mehrere Ländereien zu kaufen, bin ich der Meinung, dass ein Engländer hebräischen Glaubens nach dem geltenden Recht Englands keinen Boden besitzen kann.
\ Da es einem Juden nicht möglich ist, sich durch Landbesitz in die britische Aristokratie zu integrieren, selbst wenn er zum örtlichen Glauben konvertiert, was sollte ein Jude tun, außer durch die Macht des Geldes aufzusteigen? Wie Heine spürte auch Disraeli die Heuchelei der Christen, die es den Juden übel nahmen, dass sie keine Christen waren, sie aber weiterhin als Juden behandelten, wenn sie konvertierten, und es insgeheim sogar vorzogen, dass sie Juden blieben.
\ Laut Disraelis Biografen Robert Blake ist Sidonia „eine Kreuzung zwischen Lionel de Rothschild und Disraeli selbst“. Er stammt von einer Adelsfamilie aus Aragon ab, zu deren herausragenden Mitgliedern ein Erzbischof und ein Großinquisitor gehörten, die beide heimlich dem Judentum ihrer Väter anhingen. Sidonias Vater, wie auch Lionel de Rothschilds Vater, „machte während der Napoleonischen Kriege ein großes Vermögen mit Militärverträgen und der Versorgung der verschiedenen Armeen“. Nachdem er sich in London niedergelassen hatte, „setzte er alles, was er besaß, auf die Waterloo-Anleihe; und das Ereignis machte ihn zu einem der größten Kapitalisten Europas.“ Seit seinem siebzehnten Lebensjahr besuchte Sidonia die Fürstenhöfe der Schuldner seines Vaters und lernte die Geheimnisse der Macht kennen. „Die geheime Geschichte der Welt war sein Zeitvertreib. Es bereitete ihm großes Vergnügen, die verborgenen Motive mit den öffentlichen Vorwänden der Transaktionen zu kontrastieren.“ Disraeli selbst war laut Robert Blake „von Verschwörungen besessen“.[5]\ Robert Blake, Disraeli (1966), Faber Finds, 2010, S. 202.
\ Sidonia ist von seiner Rasse begeistert: „Alles ist Rasse – es gibt keine andere Wahrheit.“ Er weigert sich, eine Nichtjüdin zu heiraten, weil, so der Erzähler, „keine irdische Überlegung ihn jemals dazu veranlassen würde, die Reinheit der Rasse zu beeinträchtigen, auf die er stolz ist.“ Mit „Rasse“ meinte Disraeli Blutsverwandtschaft. In seinem letzten Roman Endymion (1880) schrieb er:\ Kein Mensch wird das Prinzip der Rasse gleichgültig behandeln. Es ist der Schlüssel zur Geschichte, und der Grund, warum die Geschichte oft so verwirrend ist, liegt darin, dass sie von Männern geschrieben wurde, die dieses Prinzip und all das damit verbundene Wissen nicht kennen ... Sprache und Religion machen keine Rasse aus – es gibt nur eine Sache, die eine Rasse ausmacht, und das ist Blut.\ Sidonia erzählt seinem Schützling Coningsby in Coningsby oder die neue Generation, dass die Verfolgung durch christliche Nationen die jüdische Nation niemals zerschlagen könnte.
\ Tatsache ist, dass man eine reine Rasse der kaukasischen Organisation nicht vernichten kann. Es ist eine physiologische Tatsache; ein einfaches Naturgesetz, das ägyptische und assyrische Könige, römische Kaiser und christliche Inquisitoren verblüfft hat. Keine Strafgesetze, keine körperlichen Folterungen können bewirken, dass eine überlegene Rasse in einer unterlegenen aufgehen oder von ihr vernichtet werden sollte. Die gemischten verfolgenden Rassen verschwinden, die reine verfolgte Rasse bleibt bestehen. Und im Moment, trotz Jahrhunderten oder gar Jahrzehnten der Erniedrigung, übt der jüdische Geist einen enormen Einfluss auf die Angelegenheiten Europas aus. Ich spreche nicht von ihren Gesetzen, denen Sie immer noch gehorchen; von ihrer Literatur, mit der Ihr Geist gesättigt ist, sondern vom lebendigen hebräischen Intellekt. Sie beobachten nie eine große intellektuelle Bewegung in Europa, an der die Juden nicht in hohem Maße beteiligt sind.\ Wo auch immer er reiste, fügte Sidonia hinzu, sah er jüdische Berater hinter Monarchen und Staatsoberhäuptern.
„Sie sehen also, mein lieber Coningsby, dass die Welt von ganz anderen Persönlichkeiten regiert wird, als diejenigen, die nicht hinter den Kulissen stehen, sich vorstellen können.“
In einem Sachbuch (Lord George Bentinck: A Political Biography, 1852) schrieb Disraeli:\ [Juden] sind ein lebendiger und der eindrucksvollste Beweis für die Falschheit dieser verderblichen Doktrin der Neuzeit, der natürlichen Gleichheit der Menschen. ... die natürliche Gleichheit der Menschen, die heute in Mode ist und die Form einer kosmopolitischen Bruderschaft annimmt, ist ein Prinzip, das, wenn man danach handeln könnte, die großen Rassen zersetzen und den ganzen Genius der Welt zerstören würde. ... Die angeborene Tendenz der jüdischen Rasse, die zu Recht stolz auf ihr Blut ist, ist gegen die Doktrin der Gleichheit der Menschen.[6]\ Benjamin Disraeli, Lord George Bentinck, Archibald, 1852 (archive.org), S. 496.
\ Disraeli ist eindeutig auf derselben Wellenlänge wie Moses Hess, Herzls geistiger Vater, der, nachdem er Marx (einen weiteren nominellen Konvertiten) beeinflusst hatte, zu dem Schluss kam, dass „der Rassenkrieg wichtiger ist als der Klassenkampf“ (Rom und Jerusalem, 1862). Ein gutes Beispiel für dialektische politische Manipulation ist, dass Hess Marx weiterhin heimlich unterstützte und auf dessen Bitte hin nach dem Generalkongress der Internationale in Basel (5.–12. September 1869) Verleumdungen gegen Bakunin veröffentlichte, in denen er Bakunin beschuldigte, ein Agent provocateur der russischen Regierung zu sein und „im Interesse des Panslawismus“ zu arbeiten.[7]\ Bakunins Antwort auf Französisch, „Aux citoyens rédacteurs du Réveil“, finden Sie auf Wikisource.org.\ Es ist interessant zu sehen, dass ein anderer Proto-Zionist wie Disraeli den russischen Interessen zutiefst feindlich gesinnt war.\ \ Was war Disraelis Motivation hinter der Außenpolitik, die er dem britischen Empire vermittelte? Glaubte er, dass es die offensichtliche Bestimmung der Briten sei, die Welt zu erobern? Oder sah er das britische Empire als Instrument für die überlegene Bestimmung der jüdischen Nation, wenn er sich daran erinnerte, wie Esra und Nehemia in biblischen Zeiten die Außenpolitik der Perser ausgenutzt hatten? Indem er den Suezkanal (der zwischen 1859 und 1869 von den Franzosen gegraben wurde) mit den britischen Interessen in Verbindung brachte, wollte er einfach nur die Franzosen übertrumpfen, oder legte er damit den Grundstein für das zukünftige Bündnis zwischen Israel und dem angloamerikanischen Empire? Da die Briten nun einmal den Suezkanal besaßen, mussten sie ihn verteidigen, und wie ginge das besser als mit einer befreundeten jüdischen autonomen Regierung in der Nähe in Palästina? Genau das war es, was Chaim Weizmann dreißig Jahre später den Briten schmackhaft machen wollte: „Das jüdische Palästina wäre ein Schutz für England, insbesondere in Bezug auf den Suezkanal.“[8]\ Chaim Weizmann, Trial and Error, Harper & Brothers, 1949, S. 192.
\ Und als die Israelis 1956 mit britischer und französischer Unterstützung in den Sinai einmarschierten, taten sie dies, indem sie Großbritannien erneut versprachen, die Kontrolle über den von Nasser verstaatlichten Kanal an Großbritannien zurückzugeben.
\ Disraelis Russophobie, zu der er Königin Victoria bekehrte, und seine Verteidigung der Türken, deren Massaker an den Serben und Bulgaren allgemein bekannt waren, führten zu Theorien über eine jüdische Verschwörung. William Ewart Gladstone, ein langjähriger Gegner Disraelis und selbst mehrmals Premierminister (1868–1874, 1880–1885, 1886 und 1892–1894), erklärte, dass Disraeli „die britische Außenpolitik als Geisel seiner jüdischen Sympathien nahm und mehr daran interessiert war, die Leiden der Juden in Russland und der Türkei zu lindern, als an britischen Interessen“. Die Zeitung „The Truth“ vom 22. November 1877 spielte auf die Vertrautheit Disraelis mit den Rothschilds an und vermutete „eine stillschweigende Verschwörung ... seitens einer beträchtlichen Anzahl von Anglo-Hebräern, um uns im Namen der Türken in einen Krieg zu ziehen“. Es wurde außerdem daran erinnert, dass Disraeli in einer Rede vor dem britischen Unterhaus im Jahr 1847 die Zulassung von Juden zu wählbaren Ämtern gefordert hatte, mit der Begründung, dass „der jüdische Geist einen enormen Einfluss auf die Angelegenheiten Europas ausübt“.[9]\ Stanley Weintraub, Disraeli: A Biography, Hamish Hamilton, 1993, S. 579, 547.
\ Die Königin stand, wie ein Großteil der britischen Aristokratie, bereits unter dem Bann einer modischen Theorie, die den Angelsachsen einen israelitischen Ursprung zuschrieb. Diese Theorie war erstmals zur Zeit Oliver Cromwells aufgetaucht und wurde 1840 von Pastor John Wilson in seinen Vorlesungen über das alte Israel und den israelitischen Ursprung der modernen Nationen Europas sowie 1870 von Edward Hine in The English Nation Identified with the Lost Israel neu aufgelegt. In diesem Werk erfahren wir, dass das Wort „Saxon“ von „Isaac's sons“ (Söhne Isaaks) abgeleitet ist. Diese lächerliche Theorie lieferte eine billige biblische Rechtfertigung für den britischen Kolonialismus und sogar für den Völkermord an den kolonisierten Völkern (neue Kanaaniter) durch das britische Empire (neues Israel).[10]\ André Pichot, Aux origines des théories raciales, de la Bible à Darwin, Flammarion, 2008, S. 124–143, 319.
\ Königin Victoria war glücklich, glauben zu können, dass ihre edle Abstammung auf König David zurückging, und ließ ihre Söhne beschneiden, ein Brauch, der bis heute fortbesteht. Es mag etwas Wahres an dem Gefühl der britischen Elite für ihr Judentum liegen, denn im 16. und 17. Jahrhundert hatten viele Ehen reiche jüdische Familien mit der alten, verarmten Landaristokratie vereint, so dass nach Hilaire Bellocs Schätzung „mit Beginn des 20. Jahrhunderts diejenigen der großen territorialen englischen Familien, in denen es kein jüdisches Blut gab, die Ausnahme waren“.[11]\ Hilaire Belloc, The Jews, Constable & Co., 1922 (archive.org), S. 223.
\ Die Begeisterung der Königin für das Judentum hatte aber auch viel mit dem Einfluss Disraelis zu tun, der einmal gegenüber einem Freund damit prahlte: „Jeder mag Schmeichelei, und wenn es um das Königshaus geht, sollte man sie mit einer Kelle auftragen.“[12]\ Stanley Weintraub, Disraeli: A Biography, Hamish Hamilton, 1993, S. 579, 547.
\ Der Fall Disraeli ist aufschlussreich, weil die Frage, die er aufwirft, dieselbe ist wie die Frage, die heute geopolitische Analysten in Bezug auf die Beziehung zwischen den Vereinigten Staaten und Israel spaltet: Wer führt wen an der Nase herum? Ist Israel der Brückenkopf der Vereinigten Staaten im Nahen Osten oder sind die Vereinigten Staaten, wie Zbigniew Brzezinski einmal sagte, der „dumme Esel“ Israels? Die Beantwortung dieser Frage für das Jahrhundert vor dem Zweiten Weltkrieg (als „Israel“ das internationale Judentum bedeutete) hilft bei der Beantwortung derselben Frage heute, da die symbiotische Beziehung zwischen Israel und dem Imperium erheblich gewachsen ist.
\ Die Antwort hängt vom Standpunkt des Betrachters ab. Die Zionisten haben natürlich ein Interesse daran, die Ansicht zu fördern, dass Israel den angloamerikanischen Interessen dient und nicht umgekehrt. Disraeli argumentierte vor dem britischen Parlament, dass ein jüdisches Palästina im Interesse des britischen Kolonialismus sei. Aber jüdische Zionisten haben die Dinge schon immer aus der anderen Perspektive betrachtet, und man kann kaum glauben, dass Disraeli ihre Ansicht nicht insgeheim teilte. Wenn der Held seines Romans Tancred (1847), ein Jude, der wie Disraeli zum Lord ernannt wurde, das britische Empire mit folgenden Worten verherrlicht: „Wir wollen die Welt erobern, angeführt von Engeln, um die Menschheit unter göttlicher Herrschaft glücklich zu machen“, wer verbirgt sich hinter diesem zweideutigen „wir“? Ist es dasselbe doppeldeutige „wir“, das die PNAC-Neokonservativen benutzten, um Amerika in Kriege zum Wohle Israels zu verwickeln?
\ Wenn ein britischer Jude wie Disraeli zu den Briten „wir“ sagte, war dies eine strategische Zweideutigkeit. Er traf damit den patriotischen Nerv der angelsächsischen Elite, die den gemeinsamen Glauben an die Mission des britischen Empires teilte, die Welt zu zivilisieren – Menschen wie Lord Salisbury, Mitglied von Cecil Rhodes' Round Table, der sich für eine Weltregierung durch die „britische Rasse“ einsetzte.[13]\ Carroll Quigley, The Anglo-American Establishment, From Rhodes to Cliveden (1949), Books In Focus, 1981.
\ Der britische Imperialismus und der zionistische Nationalismus wurden etwa zur gleichen Zeit geboren wie die Zwillinge Esau und Jakob und sind seit ihrer Geburt eng miteinander verflochten. Zwei Überlegungen helfen jedoch, ihre wahre Beziehung zu verstehen. Erstens reichen die ideologischen Wurzeln des Britischen Empires nicht weiter zurück als bis ins 17. Jahrhundert, während die des Zionismus mehr als zwei Jahrtausende zurückreichen. Zweitens starb das Britische Empire nach dem Ersten Weltkrieg, während der Zionismus aufblühte. Aus diesen beiden Gründen ist die Theorie, dass der Zionismus ein Nebenprodukt des britischen Imperialismus ist (nennen wir sie die Chomsky-Theorie), nicht haltbar.
\ Um die wahre Beziehung zwischen Zion und Albion zu Disraelis Zeiten zu verstehen, muss man die Macht der Rothschild-Dynastie über die britische Politik richtig einschätzen. Ohne die Rothschilds hätte Großbritannien nie die Kontrolle über den Suezkanal erlangt, der den Grundstein des britischen Empires im Nahen Osten bildete. Die Rothschilds selbst kandidierten nicht für ein politisches Amt, heirateten jedoch manchmal in eine solche Familie ein: Lord Archibald Primrose, 1886 und von 1892 bis 1894 Außenminister und 1894–1895 Premierminister, war der Schwiegersohn von Mayer Amschel de Rothschild.\ Es ist bemerkenswert, dass Theodor Herzl den zukünftigen jüdischen Staat als „aristokratische Republik“ mit „dem ersten Prinzen Rothschild“ an der Spitze sah. In einer langen Tirade in seinem Tagebuch ermahnte er die Rothschilds, ihre bösen Seelen zu erlösen, indem sie den Zionismus statt Kriege finanzierten:\ Ich weiß nicht, ob alle Regierungen bereits erkennen, welche internationale Bedrohung Ihr Weltreich darstellt. Ohne Sie können keine Kriege geführt werden, und wenn Frieden geschlossen werden soll, sind die Menschen umso mehr auf Sie angewiesen. Für das Jahr 1895 wurden die Militärausgaben der fünf Großmächte auf vier Milliarden Francs geschätzt, und ihre tatsächliche militärische Stärke in Friedenszeiten auf 2.800.000 Mann. Und diese Streitkräfte, die in der Geschichte ihresgleichen suchen, kommandieren Sie finanziell, ungeachtet der widerstreitenden Wünsche der Nationen. ... Und Ihr verfluchter Reichtum wächst immer noch. ... Aber wenn Sie sich uns anschließen, ... werden wir unseren ersten gewählten Herrscher aus Ihrem Haus nehmen. Das ist das leuchtende Leuchtfeuer, das wir auf die Spitze des fertigen Eiffelturms Ihres Vermögens setzen werden. In der Geschichte wird es so aussehen, als wäre das der Zweck des gesamten Bauwerks gewesen.[14]\ \ The Complete Diaries of Theodor Herzl, edited by Raphael Patai, Herzl Press & Thomas Yoseloff, 1960, vol. 1, pp. 163–170.\ Wie Richard Wagner jedoch einmal sagte (Judaism in Music, 1850), zogen es die Rothschilds vor, „die Juden der Könige“ zu bleiben, anstatt „die Könige der Juden“ zu sein.\ \ Wenn die Zeit für die Gründung des jüdischen Staates zu Disraelis Zeiten noch nicht reif war, dann vor allem deshalb, weil die Juden in Russland sich von Palästina ebenso wenig angezogen fühlten wie die Juden in Europa; sie wussten kaum, wo es lag. Erst kürzlich von Zar Alexander II. emanzipiert, strebten sie lediglich eine Auswanderung nach Europa oder in die Vereinigten Staaten an. Erst nach der Ermordung von Zar Alexander II. im Jahr 1881 (einen Monat vor Disraelis Tod) wurden einige von ihnen durch die Pogrome für Leon Pinskers proto-zionistischen Aufruf von 1882 empfänglich: „Wir müssen uns ein für alle Mal mit dem Gedanken abfinden, dass die anderen Nationen uns aufgrund ihres angeborenen natürlichen Antagonismus für immer ablehnen werden.“[15]\ Benzion Netanyahu, The Founding Fathers of Zionism, Balfour Books, 2012, Kindle l. 761-775.
\ Ebenfalls im Jahr 1881 begann Baron Edmond de Rothschild vom Pariser Zweig, unter der Schirmherrschaft seiner Palestine Jewish Colonization Association (PICA) Land in Palästina zu kaufen und die Ansiedlung jüdischer Siedler zu finanzieren, insbesondere in Tel Aviv. Die meisten bestehenden internationalen jüdischen Organisationen, wie B'nai B'rith (gegründet 1843 in New York) oder die Alliance Israélite Universelle (gegründet 1860 in Paris), waren jedoch der Meinung, dass Israel als verstreute Nation gut zurechtkäme und keine Pläne für Palästina habe.\ Dies änderte sich während des Ersten Weltkriegs, als ein äußerst effizientes Netzwerk aufgebaut wurde, das beide Seiten des Atlantiks verband.[16]\ Alison Weir, Against Our Better Judgment: The Hidden History of How the U.S. Was Used to Create Israel, 2014, Kindle l. 387-475.
\ Theodor Herz konzentrierte seine diplomatischen Bemühungen zunächst auf Deutschland, aber in England begannen sich die Dinge vielversprechend zu entwickeln („Der Schwerpunkt hat sich nach England verlagert“, schrieb er 1895 in sein Tagebuch), was zum Teil der Rekrutierung von Israel Zangwill zu verdanken war, der laut Benzion Netanyahu „der erste war, der in den oberen Kreisen der britischen Politik direkt über den Zionismus sprach“, insbesondere mit Lloyd George, „einem engen Bekannten Zangwills von Beginn seiner zionistischen Tätigkeit bis zu seinem Lebensende“.[17]\ Netanyahu, The Founding Fathers of Zionism, l. 2536-59.
\ Erinnern wir uns daran, dass Zangwill der erfolgreiche Autor von The Melting Pot war, einem Theaterstück, das Mischehen für Amerikaner pries. Hier besteht kein Widerspruch, denn „die gemischten verfolgten Rassen verschwinden, die reine verfolgte Rasse bleibt bestehen“, wie Sidonia sagte.\ \ Die Bedeutung von Disraelis geopolitischen Manövern wird von Historikern der Zionisten selten anerkannt, da sie oberflächlich betrachtet nicht den Weg für die Gründung des jüdischen Staates geebnet zu haben scheinen. Tatsächlich bildeten sie jedoch das unsichtbare Fundament, auf dem Herzl und Zangwill aufbauten. Und diese unsichtbare Kontinuität zeugt von der erstaunlichen generationsübergreifenden Beharrlichkeit des jüdischen Volkes, das sein jahrtausendealtes, selbsternanntes Schicksal Generation für Generation vorantreibt. Ja, es ist wirklich bewundernswert, wenn auch verheerend für die westliche Zivilisation, die durch zweitausend Jahre Christentum ahnungslos und ihres eigenen Sinns für Blut beraubt wurde. Wie der zionistische Autor Jakob Klatzkin einmal in der Zeitschrift „Der Jude“, 1916, schrieb:\ Wir bilden in uns selbst eine geschlossene juristische und geschäftliche Körperschaft. Eine starke Mauer, die wir errichtet haben, trennt uns von den Menschen in den Ländern, in denen wir leben – und hinter dieser Mauer befindet sich ein jüdischer Staat.[18]
Zitiert in Robert Edward Edmondson, The Jewish System Indicted by the Documentary Record, 1937 (archive.org), S. 15.\ \ Anmerkungen\ [1] Yuri Slezkine, The Jewish Century, Princeton University Press, 2004.\ [2] Cecil Roth, A History of the Marranos (1932), Meridian Books, 1959, S. 148.\ [3] Zitiert in Kevin MacDonald, Separation and Its Discontents: Toward an Evolutionary Theory of Anti-Semitism, Praeger, 1998, kindle 2013, l. 4732–4877.\ [4] Hannah Arendt, The Origins of Totalitarianism, Band 1: Antisemitism, Meridian Books, 1958, S. 309–310.\ [5] Robert Blake, Disraeli (1966), Faber Finds, 2010, S. 202.\ [6] Benjamin Disraeli, Lord George Bentinck, Archibald, 1852 (archive.org), S. 496.\ [7] Bakunins Antwort auf Französisch, „Aux citoyens rédacteurs du Réveil“, auf Wikisource.org.\ [8] Chaim Weizmann, Trial and Error, Harper & Brothers, 1949, S. 192.\ [9] Stanley Weintraub, Disraeli: A Biography, Hamish Hamilton, 1993, S. 579, 547.\ [10] André Pichot, Aux origines des théories raciales, de la Bible à Darwin, Flammarion, 2008, S. 124–143, 319.\ [11] Hilaire Belloc, The Jews, Constable & Co., 1922 (archive.org), S. 223.\ [12] Stanley Weintraub, Disraeli: A Biography, Hamish Hamilton, 1993, S. 579, 547.\ [13] Carroll Quigley, The Anglo-American Establishment, From Rhodes to Cliveden (1949), Books In Focus, 1981.\ [14] The Complete Diaries of Theodor Herzl, edited by Raphael Patai, Herzl Press & Thomas Yoseloff, 1960, vol. 1, pp. 163–170.\ [15] Benzion Netanyahu, The Founding Fathers of Zionism, Balfour Books, 2012, Kindle-Ausgabe, S. 761–775.\ [16] Alison Weir, Against Our Better Judgment: The Hidden History of How the U.S. Was Used to Create Israel, 2014, Kindle-Ausgabe, S. 387–475.\ [17] Netanyahu, The Founding Fathers of Zionism, S. 2536-59.\ [18] Zitiert in Robert Edward Edmondson, The Jewish System Indicted by the Documentary Record, 1937 (archive.org), S. 15.
-
 @ d076d4cc:e8d8f919
2025-02-08 12:03:03
@ d076d4cc:e8d8f919
2025-02-08 12:03:03May88 là một nền tảng kỹ thuật số tiên tiến, được thiết kế để mang lại trải nghiệm mượt mà và hiệu suất cao cho người dùng. Giao diện của May88 được tối ưu hóa để dễ sử dụng, giúp người dùng thao tác nhanh chóng và tiện lợi trên mọi thiết bị. Với hệ thống được xây dựng trên nền tảng công nghệ hiện đại, May88 đảm bảo tốc độ xử lý nhanh, ổn định và không bị gián đoạn, mang đến trải nghiệm trọn vẹn cho tất cả người dùng.
Yếu tố bảo mật luôn được đặt lên hàng đầu tại MAY88. Hệ thống bảo mật đa lớp được tích hợp để bảo vệ dữ liệu cá nhân và thông tin giao dịch của người dùng một cách an toàn. Công nghệ mã hóa tiên tiến giúp ngăn chặn các nguy cơ tiềm ẩn, đảm bảo mọi thông tin được bảo mật tuyệt đối. Đội ngũ kỹ thuật của May88 cũng liên tục cập nhật và nâng cấp hệ thống để luôn đáp ứng các tiêu chuẩn bảo mật cao nhất, mang đến sự an tâm cho người dùng khi sử dụng nền tảng.
Bên cạnh công nghệ bảo mật, May88 còn tập trung vào việc cải thiện hiệu suất của hệ thống. Các tính năng được tối ưu hóa để đảm bảo tốc độ phản hồi nhanh chóng, giúp người dùng có những trải nghiệm trơn tru mà không gặp lỗi kỹ thuật. Giao diện thân thiện, thiết kế thông minh giúp ngay cả những người mới sử dụng cũng có thể dễ dàng thao tác mà không gặp bất kỳ khó khăn nào. May88 luôn hướng đến sự hoàn hảo trong từng chi tiết để mang lại sự hài lòng cao nhất cho người dùng.
Dịch vụ hỗ trợ khách hàng tại May88 được đánh giá cao nhờ vào đội ngũ chăm sóc khách hàng chuyên nghiệp và tận tâm. Hệ thống hỗ trợ hoạt động 24/7, sẵn sàng giải đáp mọi thắc mắc và xử lý các vấn đề của người dùng một cách nhanh chóng. Người dùng có thể liên hệ qua nhiều kênh khác nhau để nhận được sự hỗ trợ tốt nhất, giúp quá trình trải nghiệm nền tảng trở nên thuận tiện và hiệu quả hơn.
Với sự kết hợp giữa công nghệ hiện đại, hệ thống bảo mật tiên tiến và dịch vụ chăm sóc khách hàng chuyên nghiệp, May88 đang khẳng định vị thế là một trong những nền tảng kỹ thuật số hàng đầu. Những cải tiến không ngừng của May88 giúp đáp ứng nhu cầu đa dạng của người dùng, mang đến trải nghiệm chất lượng cao và đáng tin cậy.
-
 @ d076d4cc:e8d8f919
2025-02-08 12:01:06
@ d076d4cc:e8d8f919
2025-02-08 12:01:06UK88 là một nền tảng kỹ thuật số tiên tiến, được thiết kế để mang đến trải nghiệm mượt mà và ổn định cho người dùng. Với giao diện trực quan, dễ sử dụng, UK88 giúp người dùng thao tác nhanh chóng trên nhiều thiết bị khác nhau mà không gặp gián đoạn. Hệ thống tối ưu hóa hiệu suất giúp nền tảng này hoạt động trơn tru, đảm bảo mọi tính năng đều vận hành chính xác và hiệu quả. Đây là yếu tố quan trọng giúp UK88 trở thành sự lựa chọn hàng đầu của những người đang tìm kiếm một nền tảng mạnh mẽ và đáng tin cậy.
Bảo mật là một trong những ưu tiên hàng đầu của UK88. Nền tảng này áp dụng công nghệ mã hóa dữ liệu tiên tiến, giúp bảo vệ thông tin cá nhân của người dùng trước mọi nguy cơ tiềm ẩn. Hệ thống bảo mật đa lớp đảm bảo rằng tất cả thông tin được lưu trữ an toàn, không bị xâm phạm bởi các tác nhân bên ngoài. UK88 cũng liên tục cập nhật và nâng cấp hệ thống để duy trì mức độ an toàn cao nhất, mang đến sự yên tâm tuyệt đối cho người dùng.
Bên cạnh yếu tố bảo mật, UK88 cũng chú trọng đến việc cải thiện hiệu suất hoạt động của nền tảng. Hệ thống được nâng cấp thường xuyên nhằm tối ưu tốc độ xử lý, giảm thiểu lỗi kỹ thuật và đảm bảo mọi thao tác đều diễn ra nhanh chóng, chính xác. Giao diện được thiết kế thân thiện với người dùng, giúp ngay cả những người mới cũng có thể dễ dàng làm quen và sử dụng nền tảng mà không gặp khó khăn.
Dịch vụ hỗ trợ khách hàng tại UK88 hoạt động 24/7, với đội ngũ chuyên nghiệp luôn sẵn sàng giải đáp mọi thắc mắc một cách nhanh chóng và hiệu quả. Người dùng có thể liên hệ qua nhiều kênh khác nhau để nhận được sự hỗ trợ tốt nhất. Với sự tận tâm và chuyên nghiệp, UK88 cam kết mang lại trải nghiệm hài lòng và đảm bảo mọi vấn đề đều được giải quyết kịp thời.
Với sự kết hợp giữa công nghệ hiện đại, hệ thống bảo mật tiên tiến và dịch vụ chăm sóc khách hàng chuyên nghiệp, UK88 ngày càng khẳng định vị thế là một nền tảng kỹ thuật số hàng đầu. Những cải tiến liên tục giúp UK88 đáp ứng được nhu cầu đa dạng của người dùng, mang đến trải nghiệm tối ưu và chất lượng cao trong mọi hoạt động.
-
 @ 472f440f:5669301e
2024-09-05 22:25:15
@ 472f440f:5669301e
2024-09-05 22:25:15https://x.com/parkeralewis/status/1831746160781938947 Here's a startling chart from an American staple, Walgreens. The convenience store and pharmacy chain has seen its stock price plummet by more than 67% this year and by more than 90% from its all time high, which was reached in 2015.
The combination of the COVID lock downs and the lax laws around theft that followed were materially detrimental to Walgreens business. The crux of their problem at the moment, however, is a double whammy of those disruptions in their business coupled with the "higher for longer" interest rate policy from the Fed over the last couple of years. As Tuur points out in the tweet above, Walgreens has $34B in debt, which means they definitely have significant interest rate payments they need to make on a monthly basis. Tuur also points out that Walgreens has very little cash compared to their debt obligations. Let's take a look at their balance sheet as of May of this year.
Less than $1B in cash for $34B debt with $67.56B in total liabilities. Even worse, their cash balance was drained by more than 27% over the course of the year between May 2023 and May 2024. As you may notice their total assets fell by more than 15% over the same period. This is because Walgreens understands the dire financial straits it finds itself in and has begun shutting down thousands of their locations across the country.
The recent efforts of Walgreens to sell off their assets to raise cash to pay down their debts seem to be completely ineffective as their cash balance is falling faster than their total assets, which is falling 7x faster than their total liabilities. These numbers are most definitely going to get worse as cascading sell pressure in commercial real estate markets (which is the bucket that Walgreens locations fall into) drive down the value of their assets. Leaving them with less cash to pay down their debts as time goes on. To make matters worse, it puts the institutions that lent money to Walgreens in a terrible position. How many commercial and investment banks has Walgreens tapped to fund their operations with expensive debt? How exposed to Walgreens is any individual lender? Could a default on some or all of their loans catch these financial institutions off sides? If it isn't Walgreens that pushes them off sides, how many more bad borrowers would it take to push them off sides?
As our good friend Parker Lewis points out, the only way the hemorrhaging can be stopped is if the Federal Reserve and Federal Government step in with bail outs in the form of massive liquidity injections via quantitative easing and other emergency measures. On top of this, the Fed and the Federal Government find themselves in a classic catch-22. If they let Walgreens fall into bankruptcy it could set off a domino effect that could exacerbate inflation. Riteaid, a similar retail convenience store and pharmacy chain, filed for bankruptcy last October and is still wading its way through that process. Part of that process has been shuttering many of their storefronts. One has to imagine that since Walgreens and Riteaid are having these problems, some of their other competitors must be feeling the pain as well. If enough of these convenience stores, which tens of millions of Americans depend on for everyday goods, find themselves in a position where they have to shut down their stores it could lead to a supply crunch. People will obviously not be able to get their goods from Riteaid or Walgreens and will flee to alternatives, exacerbating the stress on their supplies, which will drive prices higher.
This is a catch-22 because the only way to avoid this mad dash for consumer goods in the midst of a convenience store Armageddon is to re-introduce ZIRP and flood the market with freshly printed dollars, which will drive prices up as well.
Talk about a rock and a hard place. You better get yourself some bitcoin.
Final thought... Zach Bryan radio crushes.
-
 @ 472f440f:5669301e
2024-09-04 22:54:11
@ 472f440f:5669301e
2024-09-04 22:54:11For the last few months many people in bitcoin, myself included, have been focused on bitcoin's role as a macroeconomic asset. Bitcoin as a strategic reserve for the US government. Bitcoin as a strategic treasury asset for corporations. Bitcoin as a geopolitical hedge in a world that is trending toward a multi-polar power dynamic. This is where the focus has been. And for good reason. These trends will ultimately have a material effect on the price of bitcoin if they pick up steam.
However, with all of the focus on bitcoin as a strategic asset I think a couple of technical developments and trends have been overlooked. Particularly in the realm of second layer privacy. I'll touch on two of them in this letter; BOLT 12 invoices and the progression of ecash.
Yesterday afternoon the Strike (a company Ten31 is very proud to be backing) team released a blog post that detailed their journey to implementing BOLT 12 offers in their product stack. For those who are unaware of BOLT 12 and why it is important, in short, it is an upgrade to the lightning network that would make receiving bitcoin on the lightning network more private while also significantly improving the user experience. The current standard for invoicing people via the lightning network is BOLT 11, which forces users to create a unique invoice every time they want to receive bitcoin and comes with privacy tradeoffs for the party receiving bitcoin.
BOLT 12 brings with it route blinding which allows a receiver to publish a lightning offer to the network without revealing their node's public key. It also brings with it onion messaging, which allows users of the lightning network to communicate without a dependence on HTTP, which can be censored by a motivated state actor. On top of this, it enables users to create a static invoice that can be paid multiple times by multiple people. Think of a band putting their Venmo or Cash App QR code next to their tip jar on the stage. They'll be able to add a private lightning invoice their audience can pay to now.
https://strike.me/blog/bolt12-offers/
As it stands right now, Strike has only enabled BOLT 12 offers and there is work to do at the protocol layer of lightning and the different implementations of that protocol to get the full benefits of BOLT 12, but this is material progress that gets us closer to a significantly better user experience on the lightning network. If you read Strike's blog post you'll come to appreciate the collaboration between the teams working on these implementations and the companies implementing the protocol that is necessary to get these features live. Shout out to everyone who worked on this. Everyone who uses the lightning network will be better off when BOLT 12 is fully implemented.
Moving on. Earlier today the founder of the BTCPay Server open source project, Nicolas Dorier, published a blog post outlining his thoughts on how ecash has the potential to solve problems that many have tried to solve by launching their own blockchains in the past. The problem with trying to "blockchain the world" is that blockchains are very inefficient and only really work for one application; enabling a peer-to-peer digital cash system with no trusted third parties (i.e., bitcoin). However, the ultimate goals of the thousands of blockchain projects that spun up in bitcoin's wake are desirable. Cheap, private and instant transactions. The ability to trivially spin up private money tokens suited for very particular use cases. Overall great UX that makes it easy for people to realize the benefits of "blockchain technology".
The problem that has existed to date is that you don't need a blockchain for all of these things. In fact, having a blockchain for these things proves to be detrimental to their ultimate goals. Instead, what people really need is a protocol that gives you the granular control, privacy, instantaneous transactions and UX that anchors to bitcoin. This is exactly what Chaumian Mints bring to the bitcoin stack.
This is something that we've been screaming about for more than seven years in this rag. Now with ecash protocols like Cashu and Fedimint maturing, gaining traction and bringing products to market that highlight the power and flexibility of ecash systems, people are beginning to see the promise. It is only a matter of time before more and more people begin to realize this potential.
Another benefit of ecash protocols is the fact that they are siloed from each other. Ecash mints are permissionless; any one person or group of people can spin them up, offer their preferred services and maintain (or fail to maintain) their mints. The failure of one mint is not a systemic risk to other mints. This is very different from token projects that are spun up on blockchains. The last ten years have proven that individual token projects can prove to be systemic problems for individual blockchains (i.e., The DAO token on Ethereum). Being able to silo mints is the only way to ensure that the utility of ecash overall is actually scalable and robust.
Don't get so distracted by the bitcoin macro talk that you miss out on the incredible technical developments happening on top of and adjacent to bitcoin.
Final thought... Vibes are high.
-
 @ 5a261a61:2ebd4480
2025-02-02 20:42:37
@ 5a261a61:2ebd4480
2025-02-02 20:42:37Let’s be real—sticking to anything for 90 days is like trying to herd cats on espresso. You start strong, then life happens: kids, chores, or that one glass of wine that makes you forget foot rubs (#relatable). But here’s the thing: 90-day challenges aren’t about perfection. They’re about bribing your lizard brain with rewards and scaring it straight with punishments.
The Game Plan
First, pick a thing—something that makes you feel like a devoted servant or a slightly frazzled superhero. Daily foot care? Chores with a side of #FLR flair? Cool. Now, break it into chunks: 30 days (survival mode), 60 days (grind phase), and 90 days (victory lap).
Keeping up something for so long is no joke. That's why you need those little checkpoints along the way. Each milestone should feel special—30 days deserves celebration, 60 days something more meaningful, and 90 days? That's your victory dance moment.
Reality check: some days will suck, and you'll want to skip. That's where having everything planned out helps. When your brain is foggy and you're tired, you don't want to be negotiating with yourself about what counts and what doesn't. The hardest part isn't even doing the thing—it's remembering to do it every single day, until it feels wrong NOT to do it.
Why It (Maybe) Works
Three months is long enough for habits to stick, short enough to see the finish line. Plus, tying it to power exchange? Genius. Every foot rub or denied cum becomes a ritual, proof you're leveling up as a sub/human/slightly-messy adult. And let's be honest—nothing fuels devotion like a mix of structure, desperation, and the occasional humiliating punishment.
Current run
My current challenge is to get my wife/godess/object of my insatiable kinky thoughts/partner feet massaged with special cream. It's for making evyrthing soft, help nails and yadayadayada. Basically preping her feet for more instensive worshiping. She doesn't know my hidden agenda and I am not sure if I would really be into it, since I am more into being her devout toy than having foot fetish, but I think it will be all the same if I put myself juuust right. So for my rewards I have planned these? - 30 days: Tiny dopamine hit. (making little photoset of Her feet playing with my hardon… for science.)
- 60 days: Mid-tier flex. (cleaning mushed banana split off Her toes tongue only)
- 90 days: Go nuclear. (a tiny foot spa whirpool because She deserves it, damn it :D and it will create more opportunities for... you know )As for the hhip part of the sugar duo... It was easy having one for my shaving rutine, but here? Not sure and it's bad that I ave started challenge without having them prepared... May be that warrant more punishment?
TL;DR
90-day challenges are the BDSM of self-improvement: consensual, slightly painful, and weirdly addictive. Fail? Reset, adapt, try again. Win? Congrats, you’re now 10% more disciplined and 100% more bumptious on Nostr.
90days #FLR #LostCauseButStillTrying #femdom
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Veterano não é dono de bixete
"VETERANO NÃO É DONO DE BIXETE". A frase em letras garrafais chama a atenção dos transeuntes neófitos. Paira sobre um cartaz amarelo que lista várias reclamações contra os "trotes machistas", que, na opinião do responsável pelo cartaz, "não é brincadeira, é opressão".
Eis aí um bizarro exemplo de como são as coisas: primeiro todos os universitários aprovam a idéia do trote, apoiam sua realização e até mesmo desejam sofrer o trote -- com a condição de o poderem aplicar eles mesmos depois --, louvam as maravilhas do mundo universitário, onde a suprema sabedoria se esconde atrás de rituais iniciáticos fora do alcance da imaginação do homem comum e rude, do pobre e do filhinho-de-papai das faculdades privadas; em suma: fomentam os mais baixos, os mais animalescos instintos, a crueldade primordial, destroem em si mesmos e nos colegas quaisquer valores civilizatórios que tivessem sobrado ali, ficando todos indistingüíveis de macacos agressivos e tarados.
Depois vêm aí com um cartaz protestar contra os assédios -- que sem dúvida acontecem em larguíssima escala -- sofridos pelas calouras de 17 anos e que, sendo também novatas no mundo universitário, ainda conservam um pouco de discernimento e pudor.
A incompreensão do fenômeno, porém, é tão grande, que os trotes não são identificados como um problema mental, uma doença que deve ser tratada e eliminada, mas como um sintoma da opressão machista dos homens às mulheres, um produto desta civilização paternalista que, desde que Deus é chamado "o Pai" e não "a Mãe", corrompe a benéfica, pura e angélica natureza do homem primitivo e o torna esta tão torpe criatura.
Na opinião dos autores desse cartaz é preciso, pois, continuar a destruir o que resta da cultura ocidental, e então esperar que haja trotes menos opressores.
-
 @ 17538dc2:71ed77c4
2025-01-14 15:52:00
@ 17538dc2:71ed77c4
2025-01-14 15:52:00Nassim Nicholas Taleb writes:
“We cannot explain everything. We know more about what something is not than what something is. If there would have been no word for colour blue, it would still have existed in reality. It would only have been absent in linguistics. But since we don’t have a word for it, we couldn’t define or comprehend it. But we still could say what it is not. It is not orange. It’s not an elephant, etc. This method of knowledge is truer and more rigorous than positive knowledge.”In this article, I introduce practical examples of how to apply via negativa to various systems.
Recommended reading is Antifragile by N. N. Taleb.
The basic template is as follows:
What is ____ not?
Let's start with something every human should be familiar with - food.
Food
Take hot pockets. Is hot pockets food?

What is not food?
To answer this question, let's examine the contents of hot pockets.

There seem to be chemistry lab sounding ingredients ("MEDIUM CHAIN TRIGLYCERIES", "SODIUM STEAROYL LACTYLATE"), as well as food items that your great-great-great-great-great-great grandma cooked with ("SALT", "BEEF" etc.)
So What happens when we apply via negativa to the ingredients?
From 30 "ingredients" we deduce a couple foood items, or a ~90% reduction in "ingredients" by eliminating processed food slop.
 meat good
meat good bread yum
bread yumFree Discourse
Take the social media platform X.
 X consists of: leased identity, censored speech, and a tech platform for discourse. On the roadmap is social media score that will be used to determine if you can pay your bills when X launches its' bank.
X consists of: leased identity, censored speech, and a tech platform for discourse. On the roadmap is social media score that will be used to determine if you can pay your bills when X launches its' bank. What is free discourse not?
Removing the ingredient of WEF,

KYC lease hell

and censorship

we receive nostr
 .
. Nostr, to my best understanding, is not a WEF globo-homo participant, does not lease identities, and it is that much more difficult to censor wrongspeak (e.g. Netanyahu and friends are commiting genocide, and wanted as war criminals; there are two genders; there is no climate crisis; Ivermectin works).
Automobiles
Modern automobiles can be summed up in two words: "safety", and constant surveillance. Yes, advancements in safety are great - e.g. airbags, seatbelts, car frames that absorb impact energy.
However the "its for your safety" component of remote shutdown, remote control, location data selling to data brokers, insurance agents, and your local surveillance outfit is gulag tech.
!(image)[https://image.nostr.build/15befd30113614dad3fd7aac01b8771b95bd8ace9186ed4f8016eec6e886e969.jpg]
So what happens when we remove the gulag tech out of cars? That is, what is not a car?
Let's use the following definition of car:
``` A car, or an automobile, is a motor vehicle with wheels
```
Let's use the following definition of gulag:
``` The Gulag is recognized as a major instrument of political repression in the Soviet Union.
```
You get the 2024 Toyota Land Cruiser. No gulag. Airbags. Push and turn knobs. No spying, no remote control, no cameras, no satellite, no bluetooth, no wi-fi.
As an aside, it is practically impossible to import this car to the US. It's "for your safety", and "for the environment", of course.
!(image)[https://upload.wikimedia.org/wikipedia/commons/thumb/a/a1/Toyota_Land_Cruiser_16.09.20_JM_%283%29_%28cropped%29.jpg/800px-Toyota_Land_Cruiser_16.09.20_JM_%283%29_%28cropped%29.jpg]?20210328155727
Toyota Landcruiser HZJ-79 Double Cab, Johannes Maximilian
https://commons.wikimedia.org/wiki/File:Toyota_Land_Cruiser_16.09.20_JM_(3)_(cropped).jpg).Hopefully this guide has been helpful illustrating how simple and powerful it is to apply the Via Negativa approach.
Mr. Taleb, I commend you on speaking out on the Palestine genocide. I invite you to and hope one day you join anti-fragile nostr.
-
 @ 97c70a44:ad98e322
2025-01-30 17:15:37
@ 97c70a44:ad98e322
2025-01-30 17:15:37There was a slight dust up recently over a website someone runs removing a listing for an app someone built based on entirely arbitrary criteria. I'm not to going to attempt to speak for either wounded party, but I would like to share my own personal definition for what constitutes a "nostr app" in an effort to help clarify what might be an otherwise confusing and opaque purity test.
In this post, I will be committing the "no true Scotsman" fallacy, in which I start with the most liberal definition I can come up with, and gradually refine it until all that is left is the purest, gleamingest, most imaginary and unattainable nostr app imaginable. As I write this, I wonder if anything built yet will actually qualify. In any case, here we go.
It uses nostr
The lowest bar for what a "nostr app" might be is an app ("application" - i.e. software, not necessarily a native app of any kind) that has some nostr-specific code in it, but which doesn't take any advantage of what makes nostr distinctive as a protocol.
Examples might include a scraper of some kind which fulfills its charter by fetching data from relays (regardless of whether it validates or retains signatures). Another might be a regular web 2.0 app which provides an option to "log in with nostr" by requesting and storing the user's public key.
In either case, the fact that nostr is involved is entirely neutral. A scraper can scrape html, pdfs, jsonl, whatever data source - nostr relays are just another target. Likewise, a user's key in this scenario is treated merely as an opaque identifier, with no appreciation for the super powers it brings along.
In most cases, this kind of app only exists as a marketing ploy, or less cynically, because it wants to get in on the hype of being a "nostr app", without the developer quite understanding what that means, or having the budget to execute properly on the claim.
It leverages nostr
Some of you might be wondering, "isn't 'leverage' a synonym for 'use'?" And you would be right, but for one connotative difference. It's possible to "use" something improperly, but by definition leverage gives you a mechanical advantage that you wouldn't otherwise have. This is the second category of "nostr app".
This kind of app gets some benefit out of the nostr protocol and network, but in an entirely selfish fashion. The intention of this kind of app is not to augment the nostr network, but to augment its own UX by borrowing some nifty thing from the protocol without really contributing anything back.
Some examples might include:
- Using nostr signers to encrypt or sign data, and then store that data on a proprietary server.
- Using nostr relays as a kind of low-code backend, but using proprietary event payloads.
- Using nostr event kinds to represent data (why), but not leveraging the trustlessness that buys you.
An application in this category might even communicate to its users via nostr DMs - but this doesn't make it a "nostr app" any more than a website that emails you hot deals on herbal supplements is an "email app". These apps are purely parasitic on the nostr ecosystem.
In the long-term, that's not necessarily a bad thing. Email's ubiquity is self-reinforcing. But in the short term, this kind of "nostr app" can actually do damage to nostr's reputation by over-promising and under-delivering.
It complements nostr
Next up, we have apps that get some benefit out of nostr as above, but give back by providing a unique value proposition to nostr users as nostr users. This is a bit of a fine distinction, but for me this category is for apps which focus on solving problems that nostr isn't good at solving, leaving the nostr integration in a secondary or supporting role.
One example of this kind of app was Mutiny (RIP), which not only allowed users to sign in with nostr, but also pulled those users' social graphs so that users could send money to people they knew and trusted. Mutiny was doing a great job of leveraging nostr, as well as providing value to users with nostr identities - but it was still primarily a bitcoin wallet, not a "nostr app" in the purest sense.
Other examples are things like Nostr Nests and Zap.stream, whose core value proposition is streaming video or audio content. Both make great use of nostr identities, data formats, and relays, but they're primarily streaming apps. A good litmus test for things like this is: if you got rid of nostr, would it be the same product (even if inferior in certain ways)?
A similar category is infrastructure providers that benefit nostr by their existence (and may in fact be targeted explicitly at nostr users), but do things in a centralized, old-web way; for example: media hosts, DNS registrars, hosting providers, and CDNs.
To be clear here, I'm not casting aspersions (I don't even know what those are, or where to buy them). All the apps mentioned above use nostr to great effect, and are a real benefit to nostr users. But they are not True Scotsmen.
It embodies nostr
Ok, here we go. This is the crème de la crème, the top du top, the meilleur du meilleur, the bee's knees. The purest, holiest, most chaste category of nostr app out there. The apps which are, indeed, nostr indigitate.
This category of nostr app (see, no quotes this time) can be defined by the converse of the previous category. If nostr was removed from this type of application, would it be impossible to create the same product?
To tease this apart a bit, apps that leverage the technical aspects of nostr are dependent on nostr the protocol, while apps that benefit nostr exclusively via network effect are integrated into nostr the network. An app that does both things is working in symbiosis with nostr as a whole.
An app that embraces both nostr's protocol and its network becomes an organic extension of every other nostr app out there, multiplying both its competitive moat and its contribution to the ecosystem:
- In contrast to apps that only borrow from nostr on the technical level but continue to operate in their own silos, an application integrated into the nostr network comes pre-packaged with existing users, and is able to provide more value to those users because of other nostr products. On nostr, it's a good thing to advertise your competitors.
- In contrast to apps that only market themselves to nostr users without building out a deep integration on the protocol level, a deeply integrated app becomes an asset to every other nostr app by becoming an organic extension of them through interoperability. This results in increased traffic to the app as other developers and users refer people to it instead of solving their problem on their own. This is the "micro-apps" utopia we've all been waiting for.
Credible exit doesn't matter if there aren't alternative services. Interoperability is pointless if other applications don't offer something your app doesn't. Marketing to nostr users doesn't matter if you don't augment their agency as nostr users.
If I had to choose a single NIP that represents the mindset behind this kind of app, it would be NIP 89 A.K.A. "Recommended Application Handlers", which states:
Nostr's discoverability and transparent event interaction is one of its most interesting/novel mechanics. This NIP provides a simple way for clients to discover applications that handle events of a specific kind to ensure smooth cross-client and cross-kind interactions.
These handlers are the glue that holds nostr apps together. A single event, signed by the developer of an application (or by the application's own account) tells anyone who wants to know 1. what event kinds the app supports, 2. how to link to the app (if it's a client), and (if the pubkey also publishes a kind 10002), 3. which relays the app prefers.
As a sidenote, NIP 89 is currently focused more on clients, leaving DVMs, relays, signers, etc somewhat out in the cold. Updating 89 to include tailored listings for each kind of supporting app would be a huge improvement to the protocol. This, plus a good front end for navigating these listings (sorry nostrapp.link, close but no cigar) would obviate the evil centralized websites that curate apps based on arbitrary criteria.
Examples of this kind of app obviously include many kind 1 clients, as well as clients that attempt to bring the benefits of the nostr protocol and network to new use cases - whether long form content, video, image posts, music, emojis, recipes, project management, or any other "content type".
To drill down into one example, let's think for a moment about forms. What's so great about a forms app that is built on nostr? Well,
- There is a spec for forms and responses, which means that...
- Multiple clients can implement the same data format, allowing for credible exit and user choice, even of...
- Other products not focused on forms, which can still view, respond to, or embed forms, and which can send their users via NIP 89 to a client that does...
- Cryptographically sign forms and responses, which means they are self-authenticating and can be sent to...
- Multiple relays, which reduces the amount of trust necessary to be confident results haven't been deliberately "lost".
Show me a forms product that does all of those things, and isn't built on nostr. You can't, because it doesn't exist. Meanwhile, there are plenty of image hosts with APIs, streaming services, and bitcoin wallets which have basically the same levels of censorship resistance, interoperability, and network effect as if they weren't built on nostr.
It supports nostr
Notice I haven't said anything about whether relays, signers, blossom servers, software libraries, DVMs, and the accumulated addenda of the nostr ecosystem are nostr apps. Well, they are (usually).
This is the category of nostr app that gets none of the credit for doing all of the work. There's no question that they qualify as beautiful nostrcorns, because their value propositions are entirely meaningless outside of the context of nostr. Who needs a signer if you don't have a cryptographic identity you need to protect? DVMs are literally impossible to use without relays. How are you going to find the blossom server that will serve a given hash if you don't know which servers the publishing user has selected to store their content?
In addition to being entirely contextualized by nostr architecture, this type of nostr app is valuable because it does things "the nostr way". By that I mean that they don't simply try to replicate existing internet functionality into a nostr context; instead, they create entirely new ways of putting the basic building blocks of the internet back together.
A great example of this is how Nostr Connect, Nostr Wallet Connect, and DVMs all use relays as brokers, which allows service providers to avoid having to accept incoming network connections. This opens up really interesting possibilities all on its own.
So while I might hesitate to call many of these things "apps", they are certainly "nostr".
Appendix: it smells like a NINO
So, let's say you've created an app, but when you show it to people they politely smile, nod, and call it a NINO (Nostr In Name Only). What's a hacker to do? Well, here's your handy-dandy guide on how to wash that NINO stench off and Become a Nostr.
You app might be a NINO if:
- There's no NIP for your data format (or you're abusing NIP 78, 32, etc by inventing a sub-protocol inside an existing event kind)
- There's a NIP, but no one knows about it because it's in a text file on your hard drive (or buried in your project's repository)
- Your NIP imposes an incompatible/centralized/legacy web paradigm onto nostr
- Your NIP relies on trusted third (or first) parties
- There's only one implementation of your NIP (yours)
- Your core value proposition doesn't depend on relays, events, or nostr identities
- One or more relay urls are hard-coded into the source code
- Your app depends on a specific relay implementation to work (ahem, relay29)
- You don't validate event signatures
- You don't publish events to relays you don't control
- You don't read events from relays you don't control
- You use legacy web services to solve problems, rather than nostr-native solutions
- You use nostr-native solutions, but you've hardcoded their pubkeys or URLs into your app
- You don't use NIP 89 to discover clients and services
- You haven't published a NIP 89 listing for your app
- You don't leverage your users' web of trust for filtering out spam
- You don't respect your users' mute lists
- You try to "own" your users' data
Now let me just re-iterate - it's ok to be a NINO. We need NINOs, because nostr can't (and shouldn't) tackle every problem. You just need to decide whether your app, as a NINO, is actually contributing to the nostr ecosystem, or whether you're just using buzzwords to whitewash a legacy web software product.
If you're in the former camp, great! If you're in the latter, what are you waiting for? Only you can fix your NINO problem. And there are lots of ways to do this, depending on your own unique situation:
- Drop nostr support if it's not doing anyone any good. If you want to build a normal company and make some money, that's perfectly fine.
- Build out your nostr integration - start taking advantage of webs of trust, self-authenticating data, event handlers, etc.
- Work around the problem. Think you need a special relay feature for your app to work? Guess again. Consider encryption, AUTH, DVMs, or better data formats.
- Think your idea is a good one? Talk to other devs or open a PR to the nips repo. No one can adopt your NIP if they don't know about it.
- Keep going. It can sometimes be hard to distinguish a research project from a NINO. New ideas have to be built out before they can be fully appreciated.
- Listen to advice. Nostr developers are friendly and happy to help. If you're not sure why you're getting traction, ask!
I sincerely hope this article is useful for all of you out there in NINO land. Maybe this made you feel better about not passing the totally optional nostr app purity test. Or maybe it gave you some actionable next steps towards making a great NINON (Nostr In Not Only Name) app. In either case, GM and PV.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28neuron.vim
I started using this neuron thing to create an update this same zettelkasten, but the existing vim plugin had too many problems, so I forked it and ended up changing almost everything.
Since the upstream repository was somewhat abandoned, most users and people who were trying to contribute upstream migrate to my fork too.
-
 @ 7e19a1dd:ea50ba3b
2025-02-10 11:16:42
@ 7e19a1dd:ea50ba3b
2025-02-10 11:16:42Air compressors are workhorses across industries, from manufacturing plants to auto repair shops. However, keeping them running smoothly requires regular maintenance, which can be a time-consuming and costly chore. That’s where air compressor filters come into play. These simple yet vital components can help extend the life of your compressor while saving you money and headaches down the line.
What Do Air Compressor Filters Actually Do?
Air compressors suck in air from their surroundings, and that air isn’t always clean. It can carry dirt, moisture, and even tiny particles that can damage your compressor's internal parts. Filters act as the gatekeepers, trapping contaminants before they wreak havoc.
Without a good filter, dirt and debris can clog valves and reduce efficiency. Even worse, it can lead to costly repairs—or worse, a full-blown breakdown. Filters also remove moisture, preventing rust and corrosion in your compressor and connected equipment.
Less Maintenance, More Savings
Regular maintenance on an air compressor is inevitable, but filters significantly cut down the frequency of those tune-ups. Clean air means fewer clogs and less wear and tear on moving parts. As a result, you’ll need fewer repairs and part replacements over time.
And let’s not forget energy efficiency. When an air compressor operates with clean air, it doesn’t have to work as hard. This reduced workload translates into lower energy bills. Over time, this can add up to significant savings.
Filters Protect Your Investment
Air compressors aren’t cheap, and replacing one can feel like a punch to the wallet. Using high-quality air compressor filters protects your investment by keeping the equipment running at peak performance. Think of it like regularly changing your car’s oil. It’s a small, affordable step that prevents big problems later.
Save Time and Effort
No one enjoys unscheduled downtime, especially when deadlines are looming. A well-maintained compressor equipped with a proper filter is far less likely to break down unexpectedly. That means fewer interruptions and more time to focus on your work. And here’s another bonus: replacing filters is quick and easy. Compared to the hours it can take to clean or repair a compressor, swapping out a filter is a breeze.
Choosing the Right Filter
Not all filters are created equal. Make sure you choose one that matches your compressor’s specifications. If you’re unsure, check your user manual or ask a professional. Investing in a high-quality filter might cost a little more upfront, but it will pay off in the long run.
Final Thoughts
Air compressor filters are a small but mighty tool in keeping your equipment running smoothly. They cut down on maintenance, protect your compressor, and save you both time and money. By making filters a regular part of your maintenance routine, you’ll not only extend the life of your compressor but also improve its efficiency. That’s a win-win for your wallet and your workflow. So, the next time you fire up your air compressor, make sure its filter is up to the task. You’ll thank yourself later!
-
 @ dbb19ae0:c3f22d5a
2025-02-08 10:27:12
@ dbb19ae0:c3f22d5a
2025-02-08 10:27:12- Downloading the linux package (1.8GB) https://cortex.so/docs/installation
- Installing Cortex on linux is done via dpkg
note: it requires 2 linux packages (openmpi-bin and libopenmpi-dev)
sudo apt-get install openmpi-bin libopenmpi-devprior to runsudo dpkg -i cortex-1.0.9-linux-amd64-local-installer.deb -
When running Cortex,
cortex starta local implementation will be running on http://127.0.0.1:39281 -
Using python it is possible to run queries make sure the model name is correct you can double check the value using:
cortex ps
Now the python program to run one little query: ``` python import requests
url = "http://127.0.0.1:39281/v1/chat/completions"
headers = {"Content-Type": "application/json"}
payload = { "model": "tinyllama:1b-gguf", "messages": [ { "role": "user", "content": "Write a joke" } ], "stream": False, "max_tokens": 128, "stop": ["End"], "frequency_penalty": 0.2, "presence_penalty": 0.6, "temperature": 0.8, "top_p": 0.95, }
response = requests.post(url, json=payload, headers=headers)
print(response.json()) ```
-
 @ e5272de9:a16a102f
2024-08-31 20:23:59
@ e5272de9:a16a102f
2024-08-31 20:23:59The GrapeRank algorithm, like the PageRank algorithm, takes as input a graph, composed of nodes and edges, and composes "importance" scores for each node based on the topology of the graph. This equation is currently implemented at brainstorm and uses follows and mutes to calculate a trust score G (also called an "influence" score) in the range [0, 1] for each user in your nostr network.
This is the GrapeRank equation:
- G, c, and r in this equation are each scalars in the interval [0, 1]
- G represents the grapevine score (also called the "influence") of v, as seen from the vantage point of o
- r represents the average rating of v by o's grapevine
- c represents the degree of confidence in the average rating r
- the subscript always represents the thing (user, product, etc) being evaluated
- the superscript always represents the "observer," the point of reference from which we view and interpret the world
This is the same equation in expanded format:
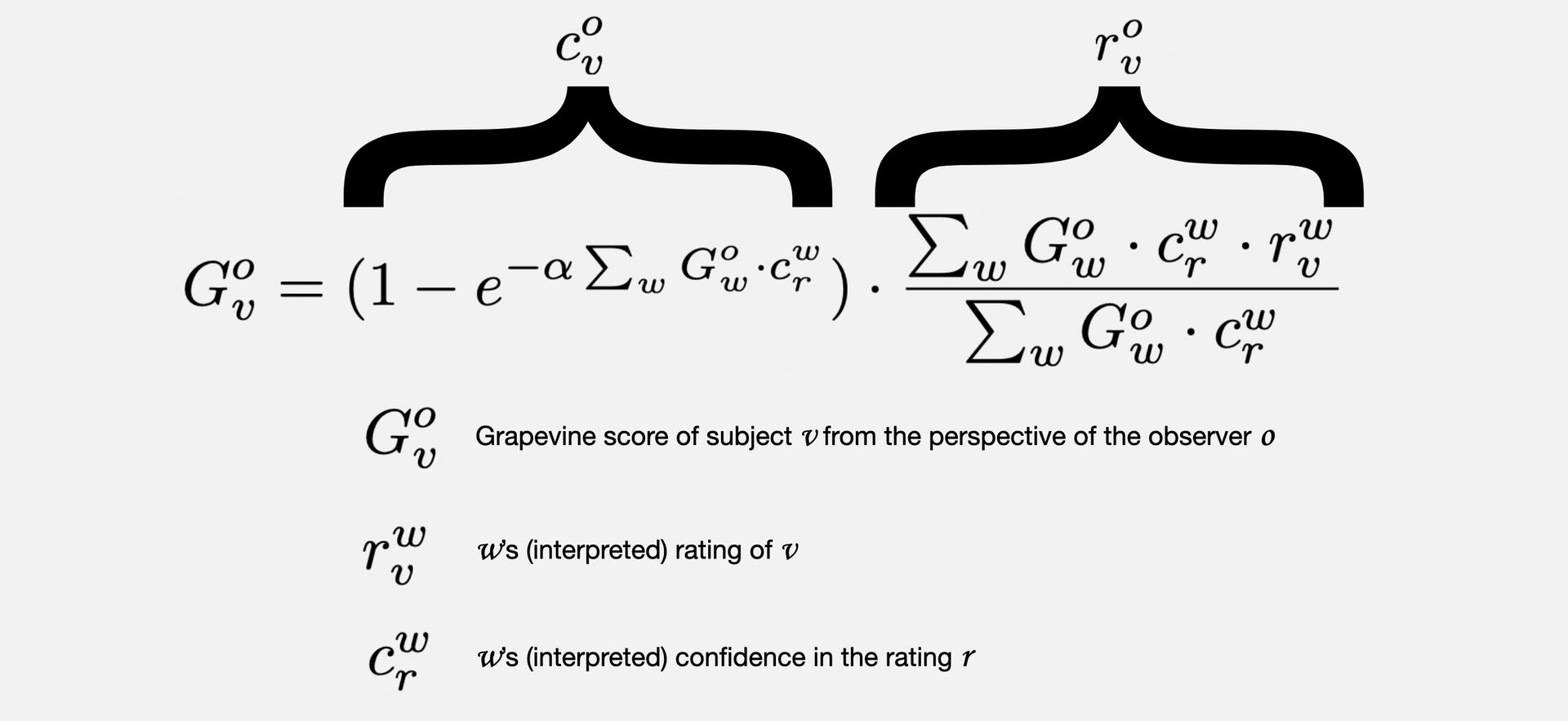
- The grapevine score of v on the left, G_v, is weighted using the grapevine score (but of each w) on the right, G_w
- These calculations are iterated until all G values converge
- r^o_v (the right half) is the weighted average
- c^o_v (the left half) is the confidence in that weighted average
- The r^w_v are the ratings being averaged together; they are inferred from follows and mutes by interpreting a follow as a score of 1 (probably not a bot), a mute as a score of 0 (probably a bot)
- The c^w_r are the confidences in the r^w_v; a follow is interpreted to have a confidence of 5 percent, a mute to have a confidence of 10 percent. (These are adjustable settings at brainstorm.)
- The sum over G * c, which appears twice in the above equation, is called the "input" and is an unbounded, nonnegative scalar which represents "the amount of trusted input" that goes into the calculation
- The formula is designed so that as the input (the number of ratings from trusted sources) increases to infinity, the confidence c^o_v approaches 1 (100 percent) asymptotically. This map from input onto confidence, which employs a nonlinear equation, is necessary to ensure that G remains within the [0, 1] interval even as input increases to infinity.
- alpha is a nonnegative scalar value that determines how "quickly" the confidence c^o_v approaches 1 (100 percent) as trusted input increases. Decreasing the value for alpha makes the equation more "rigorous" because it will take more trusted input to achieve any given degree of confidence. (Alpha is another user-adjustable setting at brainstorm.)
To perform the above calculations: 1. For the "seed" user (the observer o, i.e. the logged-in user), fix average, confidence, and G (influence) to unity. These values will not change. 2. For all other users, initialize average, confidence, and influence scores to zero. 3. Iterate through all users to calculate average, confidence, and influence scores. In the first iteration, the follows of the logged-in users will obtain nonzero scores. In the second iteration, their follows will obtain nonzero scores. And so on. 4. Continue iteration until all values converge.
Intuition tells us that convergence is guaranteed by the requirement that for each rating, the rating and its associated confidence are scalar values between 0 and 1. G will therefore also always also be a number between 0 and 1. Not shown: at brainstorm and in general recommended practice, the above equation also employs a scalar value between 0 and 1 called the "attenuation factor," defaulted at 0.8 but adjustable by the user, which causes influence scores G^o_v to diminish as the number of hops between o and v increases.
Intended usage
G is designed to be used as a weight when calculating weighted averages, tallying votes, etc. It is highly effective at eliminating bots without turning into a popularity contest.
Interpretation
G^o_v is a recommendation, to you by your grapevine, that reflects in numerical form how much "attention" you should pay to pubkey v in the given context (if a context is given).
- G^o_v = 0 means that pubkey v is not worthy of your attention, because v is probably a bot
- G^o_v = 1 means that pubkey v is worthy of your full attention, because b is probably not a bot
- Values between 0 and 1 mean the grapevine isn't absolutely certain one way or another, whether because of scant information (some follows by trusted sources, but not many) or conflicting information (combination of follows and mutes)
Note that if a bad actor spins up a large number of bots and uses them to follow himself, those follows will be completely ignored, because those bots will have a zero trust score G.
Change of context
The set of ratings r can be generated from any data source, regardless of format. By selecting different ratings datasets, we can generate grapevine scores to reflect different contexts. Example: collect emoji reactions to content on Topic X and infer a fire emoji as a rating of 2, rocket as a 3, thumb down as a 0, etc. The resulting G, which will take values between 0 and 3, is now interpreted to apply only to Topic X.
Compact notation
The above equation can be written more succinctly:
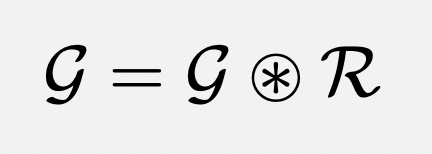
where G represents the baseline grapevine score, and R represents the dataset generated from follows and mutes.
Note that we can use a different G on the left versus on the right:
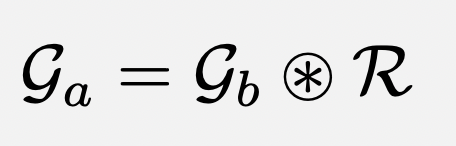
The same relationship can be expressed using arrow notation:
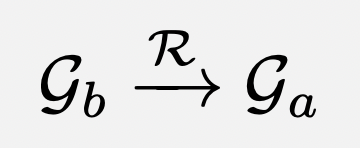
The above relationship in arrow notation should be read to mean that the set of scores G_a are calculated using dataset R which has been authored exclusively by members represented by G_b. In other words, the ratings R are weighted using the set of scores G_b.
Note that the dataset R is generated via interpretation of preexisting content. We can use any content that we can find. There is no requirement or expectation that users will necessarily generate ratings in a format convenient for input into the grapevine. The process of "interpretation" takes care of that, by "translating" existing data into a format suitable for use by the grapevine.
Note also that grapevine scores G may refer to anything in any context: trust scores for users, quality scores for products, etc.
Concerns about convergence
If the G_a and G_b represent the same context (G_a = G_b), the relationship is said to be "recursive," and calculations are iterated until they converge.
If G_a != G_b, the relationship is not recursive, and a single iteration through each pubkey is all that is needed. This means that we can allow G_a and / or G_b to be greater than 1 with no need to worry about convergence.
Worldviews
Arrow notation allows us to link trust calculations in chains:

A graph of grapevine scores G_i linked via arrow notation is called a worldview.
For example, consider the following worldview: * G_a is the baseline nostr trust score, as described above, intended to separate bots from real users * G_b is a label applied to nostr users, intended as a label for bitcoiners (as opposed to nocoiners or shitcoiners) * G_c is a quality score applied to hardware wallets
The purpose of the above worldview is so that I can get a ranked list of hardware wallets and I can be reasonably sure that the list is curated by bitcoiners whose instincts on this topic I value more highly than the general population.
Worldviews can contain any desired number of nodes, connected by any desired number of arrows, and so can be as complex as desired.
Obviously, the construction of a worldview reflects the value system of the person who uses it, with the above worldview offered as a reflection of maximalist values and beliefs. Worldviews can be codified and submitted to the wider community. One's grapevine can even be used to select individuals who should be trusted to edit or construct worldviews.
Computational cost
The methods described above are expected to be too time consuming and computationally expensive to do all of them on the fly on the front end. Notably, the ones that are recursive. Non-recursive computations, however, can be done on the front end, provided recursive calculations have been done ahead of time and are readily available. It is anticipated that the value added by well-crafted worldviews will more than justify the requisite costs.
-
 @ dff95033:862fbf40
2025-02-08 03:01:06
@ dff95033:862fbf40
2025-02-08 03:01:06Como posso dizer? Essas 25 pautas bienais do Ministério da Fazenda (MF) deveriam ter sido liberadas, no mínimo, em dezembro de 2024. Afinal, são assuntos complexos que exigem tempo para a nação — nós, o povo brasileiro — e o Congresso se debruçarem sobre essas pautas com a devida calma. Algo que, sabemos, é um luxo raro na política brasileira.
Mas, mesmo que o MF entregasse essas pautas em dezembro de 2024, já seria um prazo apertado. Agora, liberar as bienais no meio do primeiro trimestre de 2025? Isso só pode ser chamado de uma coisa: pura pilantragem. Não há outro nome. Com um cronograma tão curto, as pautas mal terão tempo para serem escrutinadas e, com certeza, passarão batidas. E o pior: muitas dessas pautas ainda estão em fase de elaboração e discussão. Ou seja, nem sabemos se serão viáveis ou se vão sair conforme o previsto nesse documento.
É uma lambança sem tamanho. Se um plano de negócios fosse apresentado assim a um investidor ou a uma instituição de crédito, com 100% de certeza seria ridicularizado e desconsiderado na hora. Não consigo visualizar o Congresso tendo tempo hábil para lidar com algo desse tipo.
O documento contém gráficos, mas, como não possuem referências de dados, desconsiderei-as. Afinal, sem os dados, para mim são apenas figurinhas para enfeitar o documento.
O documento é simples: uma planilha com 25 ações para serem implementadas no biênio de 2025 a 2026, divididas em três eixos, a saber:
1. Estabilidade Macroeconômica: Política Fiscal e Justiça Tributária
O eixo que promete arrumar a bagunça fiscal.
2. Melhoria do Ambiente de Negócios
O eixo que promete desburocratizar e modernizar o ambiente de negócios.
3. Novo Brasil: Plano de Transformação Ecológica
O eixo que promete implementar pautas Ambientais, Sociais e de Governança (ASG = ESG).
Montei uma tabela para simplificar. Espero que seja de boa apreciação:
| Nº | Ação | Objetivo | Andamento | | --- | --- | --- | --- | | 1 | Fortalecimento do Arcabouço Fiscal | Garantir crescimento sustentável e controle da dívida pública. | Lei Complementar 200/2023 aprovada; medidas em implementação. | | 2 | Reforma Tributária sobre o Consumo | Simplificar impostos e desonerar exportações e investimentos. | EC 132/2023 promulgada; implantação em andamento. | | 3 | Regulamentação da Reforma Tributária | Definir gestão do IBS, imposto seletivo e fundos constitucionais. | PLP 108/2024 em tramitação no Senado. | | 4 | Reforma Tributária sobre a Renda | Isentar IRPF para rendas até R$ 5 mil e tributar os mais ricos. | A ser enviado ao Congresso em 2025. | | 5 | Limitação dos Supersalários | Reduzir desigualdades salariais no setor público. | EC 135/2024 promulgada; projeto de lei a ser enviado em 2025. | | 6 | Reforma da Previdência dos Militares | Reduzir disparidades com o regime civil. | PL 4920/2024 em tramitação. | | 7 | Conformidade Tributária e Aduaneira | Valorizar bons contribuintes e penalizar devedores persistentes. | PL 15/2024 em tramitação. | | 8 | Aprimoramento da Lei de Falências | Melhorar governança do processo falimentar. | PL 3/2024 aprovado na Câmara; aguardando Senado. | | 9 | Proteção a Investidores no Mercado de Capitais | Proteger investidores minoritários. | PL 2925/2023 aguardando relator na Câmara. | | 10 | Consolidação Legal das Infraestruturas Financeiras | Promover eficiência no sistema financeiro. | PL 2926/2023 aprovado na Câmara; aguardando Senado. | | 11 | Resolução Bancária | Aprimorar regimes de liquidação de instituições financeiras. | PLP 281/2019 aguardando apreciação. | | 12 | Mercado de Crédito | Desjudicializar execuções e modernizar operações de crédito. | PL 6204/2019 em tramitação no Senado; Discução e elaboração no Executivo. | | 13 | Regulamentação das Big Techs | Coibir práticas anticoncorrenciais no mercado digital. | Em elaboração pelo Executivo. | | 14 | Modernização do Marco Legal de Preços de Medicamentos | Revisar regras de precificação de medicamentos. | Em análise pela CMED. | | 15 | Pé-de-Meia | Permitir que alunos invistam benefícios do ensino médio. | Em elaboração pelo Executivo. | | 16 | Modernização do Regime de Concessões e PPPs | Aprimorar contratos de serviços públicos e parcerias. | PL 7063/2017 em tramitação na Câmara. | | 17 | Títulos Sustentáveis | Financiar projetos ecológicos com títulos verdes. | Duas emissões realizadas (US$ 4 bilhões). | | 18 | Mercado de Carbono | Criar mercado regulado de carbono no Brasil. | Lei 15.042/2024 sancionada; regulamentação em preparação. | | 19 | Leilões do EcoInvest | Atrair investimentos estrangeiros em projetos sustentáveis. | Primeiro leilão realizado; novos em preparação. | | 20 | Compra Pública com Conteúdo Nacional | Exigir produção local em compras públicas. | Regras de conteúdo local em implementação. | | 21 | Fundo Internacional de Florestas | Criar fundo global para preservação de florestas tropicais. | Em discussão no G20. | | 22 | Taxonomia Sustentável Brasileira | Classificar atividades e projetos sustentáveis. | Em consulta pública; implementação prevista para 2025. | | 23 | Marco Legal da Inteligência Artificial | Promover desenvolvimento responsável da IA. | PL 2338/2023 aprovado no Senado; aguardando Câmara. | | 24 | Plano Safra e Renovagro | Aprimorar crédito para práticas agrícolas sustentáveis. | Resoluções CMN já expedidas. | | 25 | Plataforma de Investimentos Sustentáveis (BIP) | Conectar projetos sustentáveis com financiadores. | Projetos cadastrados totalizam US$ 10 bilhões. |
A onde chegamos
Acompanhar, destrinchar e analisar cada uma das 25 pautas em tempo hábil é uma tarefa hercúlea – e, sinceramente, quase impossível para uma pessoa só. Afinal, quando se trata de política e economia, tudo muda rápido demais. Provavelmente, quando eu terminar de escrever este artigo, metade das propostas já terá sido alterada, adiada ou esquecida em alguma gaveta.
Mas, como o objetivo aqui é compartilhar conhecimento e reflexões, decidi registrar minhas impressões e notas até onde pude chegar nessas poucas horas de análise. Se você, leitor, se interessar por mergulhar mais fundo no tema, compartilho abaixo o conteúdo completo do documento, organizado para facilitar sua leitura. E, claro, ao final, as referências com os links para você conferir as fontes originais.
Afinal, em um país onde as regras do jogo mudam a cada minuto, a melhor arma que temos é a informação. E, como diz o ditado: “Quem avisa, amigo é.”
Hora do jabá! Toda ajuda é bem-vinda. Se gostou, comente, compartilhe e, se puder, ajude com o café — e sério, você já viu o preço do café?
MINISTÉRIO DA FAZENDA — INICIATIVAS PARA O BIÊNIO DE 2025 À 2026
ESTABILIDADE MACROECONÔMICA: POLÍTICA FISCAL E JUSTIÇA TRIBUTÁRIA

1. Fortalecimento do arcabouço fiscal, para assegurar expansão sustentável do PIB, desemprego e inflação baixos e estabilidade da dívida
- Resumo: adequação da dinâmica de crescimento de gastos aos limites do Novo Arcabouço Fiscal, para fortalecê-lo e assegurar sustentabilidade da dívida pública.
- Status: aprovada a Lei Complementar 200/2023; Pacote de gastos aprovado no fim de 2024 a partir da promulgação da EC 135/2024, Lei Complementar 211/2024 e Lei 15.077/2024; implementação e acompanhamento de medidas aprovadas e política permanente de revisão de despesas.
2. Início da implantação da reforma tributária sobre o consumo
- Resumo: mudança na sistemática de tributação sobre consumo, simplificando o sistema e desonerando exportações e investimentos.
- Status: promulgada a Emenda Constitucional 132/2023, sancionada a Lei Complementar 214/2025 e início das etapas de implantação administrativa.
3. Regulamentação da reforma tributária: Lei de Gestão e Administração do IBS, Fundos e Imposto Seletivo
- Resumo: outros aspectos da EC 132/2023 ainda exigem regulamentação, como a gestão federativa do IBS, as regras para o imposto seletivo e os fundos constitucionais definidos pela reforma tributária.
- Status: PLP 108/2024 em tramitação no Senado Federal; Projeto de lei do imposto seletivo e projetos de lei de regulamentação dos Fundos serão enviados em 2025.
4. Reforma tributária sobre a renda com isenção de IRPF para quem ganha até R$ 5 mil e tributação sobre o topo da pirâmide de renda
- Resumo: reforma dos impostos diretos para corrigir assimetrias no IRPF, tornando-o mais progressivo e redutor de desigualdades. A reforma propõe isenção de IRPF para renda até R$ 5 mil e a implementação de um imposto mínimo sobre contribuintes de renda muito alta, assegurando que os brasileiros no topo da pirâmide contribuam de forma justa.
- Status: a ser enviado ao Congresso Nacional em 2025.
5. Limitação dos supersalários
- Resumo: medida para combater supersalários no setor público, reduzindo desigualdades entre carreiras. Institucionalizada pela EC 135/2024, que determina que apenas descontos expressamente previstos em lei podem excepcionar o limite remuneratório.
- Status: EC 135/2024 promulgada e projeto de lei a ser enviado em 2025.
6. Reforma da previdência dos militares
- Resumo: alterações na previdência militar para reduzir disparidades com os regimes civis, incluindo a definição de idade mínima para reserva remunerada, contribuições para assistência médico-hospitalar e social, além de eliminar a pensão por "morte ficta" e a reversão de pensão para beneficiários de ordens subsequentes.
- Status: PL 4920/2024 em tramitação no Congresso Nacional.
7. Projeto de lei da conformidade tributária e aduaneira, com valorização do bom contribuinte e responsabilização do devedor contumaz
- Resumo: proposta que corrige distorções na arrecadação, valoriza contribuintes cumpridores e penaliza devedores persistentes, melhorando a gestão fiscal da União. Inclui programas de conformidade e estabelece condições para benefícios fiscais.
- Status: PL 15/2024 em tramitação no Congresso Nacional.
MELHORIA DO AMBIENTE DE NEGÓCIOS

8. Aprimoramento da Lei de Falências
- Resumo: aprimora a governança do processo falimentar, com designação da figura do gestor fiduciário e a criação do plano de falências.
- Status: aprovado o PL 3/2024 na Câmara dos Deputados. Aguardando apreciação no Senado Federal.
9. Fortalecimento da proteção a investidores no mercado de capitais
- Resumo: aprimora mecanismos de proteção a investidores minoritários no mercado de capitais e aperfeiçoa regras contra eventuais prejuízos causados por acionistas controladores.
- Status: PL 2925/2023 aguardando designação de relator na Câmara dos Deputados.
10. Consolidação legal das infraestruturas do mercado financeiro
- Resumo: dispõe sobre as instituições operadoras de infraestruturas do mercado financeiro no âmbito do Sistema de Pagamentos Brasileiro, promovendo maior eficiência nas operações entre as instituições financeiras, com menores custos e mais segurança aos consumidores finais.
- Status: aprovado o PL 2926/2023 na Câmara dos Deputados. Aguardando apreciação pelo Senado Federal.
11. Resolução bancária
- Resumo: aprimora e homogeniza regimes de estabilização e liquidação de instituições do sistema financeiro, securitário e do mercado de capitais.
- Status: PLP 281/2019 aguardando apreciação na Câmara.
12. Mercado de crédito
- Resumo:
- desjudicialização da execução civil de título executivo judicial e extrajudicial;
- operacionalização das operações de crédito consignado por meio de plataforma digital;
- uso de fluxo de pagamentos no Pix e outros recebíveis em garantia de operações de crédito, especialmente para MPEs;
- ecossistema único para registro e uso de ativos financeiros como garantia em operações de crédito (open asset).
- Status:
- PL 6204/2019 em tramitação no Senado Federal;
- em elaboração pelo Executivo;
- e 4. regulamentação e operacionalização em discussão no Executivo.
13. Regulamentação econômica das Big Techs
- Resumo: projeto de Lei para incentivar a concorrência ao dotar o poder público de ferramentas mais adequadas para coibir práticas anticoncorrenciais nos mercados digitais.
- Status: em elaboração pelo Executivo.
14. Modernização do marco legal de preços de medicamentos
- Resumo: revisão da regulação da Câmara de Regulação do Mercado de Medicamentos (CMED), para modernizar regras de precificação, contemplando medicamentos de alto custo e inovações feitas pela indústria nacional, buscando aprimorar a gestão dos recursos públicos, especialmente no atendimento de demandas judiciais.
- Status: proposta em análise pela CMED (Poder Executivo).
15. Pé-de-Meia: permissão ao aluno investir em poupança ou títulos do Tesouro
- Resumo: permite ao aluno investir antecipadamente os benefícios que seriam resgatados somente ao final do ensino médio, a fim de promover a educação financeira e possibilitar o aumento dos benefícios com a rentabilidade auferida no período.
- Status: em elaboração pelo Executivo.
16. Modernização do regime de concessão e permissão da prestação de serviços públicos e das parcerias público-privadas
- Resumo: reforma substancial do marco legal para aprimorar o equilíbrio econômico dos contratos, melhorar o processo de seleção das empresas, prever repartição objetiva de riscos e aprimorar a segurança jurídica dos contratos.
- Status: Projeto de Lei 7063/2017 em tramitação na Câmara dos Deputados.
NOVO BRASIL: PLANO DE TRANSFORMAÇÃO ECOLÓGICA

17. Nova emissão de títulos sustentáveis, trazendo recursos ao Fundo Clima
- Resumo: títulos da dívida pública com critérios de sustentabilidade para financiar atividades da transformação ecológica com taxa de juros competitivas.
- Status: Duas emissões já realizadas, totalizando US$ 4 bilhões. Novas rodadas de emissões planejadas.
18. Avanço na implantação do mercado de carbono (governança e decreto regulamentador)
- Resumo: criação do mercado regulado de carbono no Brasil, com teto de emissões e mecanismo de precificação.
- Status: sancionada a Lei 15.042/2024, em preparação as regras de governança e a regulamentação da lei.
19. Novos Leilões do EcoInvest
- Resumo: programa de proteção cambial e mobilização de investimentos estrangeiros em projetos sustentáveis.
- Status: sancionada a Lei 14.995/2024 e realizado o primeiro leilão do programa com ampla adesão. Em preparação os novos leilões do programa.
20. Compra pública com conteúdo nacional e programa de desafios tecnológicos para a transformação ecológica
- Resumo: exigência de que parte dos equipamentos e serviços sejam produzidos no Brasil em casos de compras e financiamentos públicos e uso do poder de compra para desenvolver inovações tecnológicas.
- Status: contratações do PAC, Fundo Clima e fundos regionais passam gradualmente a utilizar regras de conteúdo local. Está em gestação a criação de um programa de desafios tecnológicos associados à transformação ecológica.
21. Estruturação do Fundo Internacional de Florestas
- Resumo: criação de fundo global cujos rendimentos sejam repassados a países que preservam suas florestas tropicais.
- Status: incluído na Declaração Final do G20, está em discussão multilateral para viabilizar sua implantação.
22. Implementação da Taxonomia Sustentável Brasileira
- Resumo: criação de sistema de classificação de atividades, projetos e ativos# que contribuem para objetivos climáticos e sociais.
- Status: texto está em consulta pública. Implementação prevista a partir do segundo semestre de 2025.
23. Marco legal da inteligência artificial e política de atração de datacenter
- Resumo: conjunto de medidas para promover o desenvolvimento responsável da Inteligência Artificial e atração de datacenters sustentáveis, aproveitando o potencial de energia renovável, para impulsionar a produtividade da economia nacional.
- Status: marco legal de IA foi aprovado no Senado Federal em 2024 (PL 2338/2023) e deve começar discussão na Câmara. O Governo está elaborando a Política Nacional de Datacenters.
24. Plano Safra e Renovagro: aprimoramento dos critérios de sustentabilidade
- Resumo: melhora das condições de crédito para práticas agrícolas sustentáveis e regularização do cadastro ambiental, além de assistência técnica.
- Status: resoluções CMN já expedidas e novas medidas de aprimoramento nos próximos Planos Safra.
25. Consolidar o mapa de investimentos sustentáveis na BIP (Plataforma de Investimentos para a Transformação Ecológica no Brasil)
- Resumo: plataforma gerida pelo BNDES que conecta projetos em bioeconomia, indústria de baixo carbono e transição energética com ampla rede de financiadores.
- Status: projetos já cadastrados totalizam US$ 10 bilhões. Está em curso parceria com CDESS/PR e Cepal para mapeamento e estruturação de novos projetos.
REFERÊNCIAS
AGÊNCIA CÂMARA DE NOTÍCIAS. Motta recebe de Haddad prioridades do governo na agenda econômica. Câmara dos Deputados. Disponível em: https://www.camara.leg.br/noticias/1130838-motta-recebe-de-haddad-prioridades-do-governo-na-agenda-economica/. Acesso em: 7 fev. 2025.
AGÊNCIA CÂMARA DE NOTÍCIAS. Ministro da Fazenda diz que projeto sobre isenção do IR já está pronto. Câmara dos Deputados. Disponível em: https://www.camara.leg.br/noticias/1131045-ministro-da-fazenda-diz-que-projeto-sobre-isencao-do-ir-ja-esta-pronto/. Acesso em: 7 fev. 2025.
AGÊNCIA SENADO FEDERAL. Senado já analisa temas prioritários para a agenda econômica do governo. Senado Federal. Disponível em: https://www12.senado.leg.br/noticias/materias/2025/02/06/senado-ja-analisa-temas-prioritarios-para-a-agenda-economica-do-governo. Acesso em: 7 fev. 2025.
BRASIL. Ministério da Fazenda. Iniciativas para o Benefício de 2025 à 2026. Disponível em: https://www.camara.leg.br/midias/file/2025/02/25-iniciativas-do-mf-em-2025-e-2026.pdf. Acesso em: 7 fev. 2025.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28On "zk-rollups" applied to Bitcoin
ZK rollups make no sense in bitcoin because there is no "cheap calldata". all data is already ~~cheap~~ expensive calldata.
There could be an onchain zk verification that allows succinct signatures maybe, but never a rollup.
What happens is: you can have one UTXO that contains multiple balances on it and in each transaction you can recreate that UTXOs but alter its state using a zk to compress all internal transactions that took place.
The blockchain must be aware of all these new things, so it is in no way "L2".
And you must have an entity responsible for that UTXO and for conjuring the state changes and zk proofs.
But on bitcoin you also must keep the data necessary to rebuild the proofs somewhere else, I'm not sure how can the third party responsible for that UTXO ensure that happens.
I think such a construct is similar to a credit card corporation: one central party upon which everybody depends, zero interoperability with external entities, every vendor must have an account on each credit card company to be able to charge customers, therefore it is not clear that such a thing is more desirable than solutions that are truly open and interoperable like Lightning, which may have its defects but at least fosters a much better environment, bringing together different conflicting parties, custodians, anyone.
-
 @ 5a261a61:2ebd4480
2025-01-30 09:37:26
@ 5a261a61:2ebd4480
2025-01-30 09:37:26The idea of the Bean Bag Game is quite ingenious. I read about it on a BDSM-positive blog. Here’s how it works:
-
Setup:
-
Take a small cloth bag and add 10 white beans (rewards/pleasure) and 10 black beans (punishment/discomfort).
-
When it’s time to play, draw two beans:
-
First bean (the tone): Determines if the activity will be pleasant (white) or uncomfortable (black).
-
Second bean (the task): Decides whether you get a reward (white) or punishment (black).
-
Combination Interpretations:
-
Black + Black\ "No fun, just work."
-
Boring/challenging tasks you’d normally postpone: window cleaning, scrubbing bathroom tiles, polishing shoes.
-
Could also mean no playtime (e.g., "Go straight to bed"). Pure duty – no pleasure, only discipline.
-
White + Black\ "Work with a twist."
-
Punishment or chores, but with a kinky edge:
-
Clean the bathroom wearing a vibrating butt plug.
-
Wash dishes with nipple clamps; add a clothespin to your body for every minute over the time limit.
-
-
Still no orgasms – the black bean ensures denial.
-
Black + White\ "Pleasure with pain (or humiliation)."
-
Mix stimulation and discomfort:
-
Ride a dildo with weighted nipple clamps.
-
Give a "lap dance" to a teddy bear with a strapon.
-
Chat online as a "perfect plaything" for others without touching yourself.
-
-
Again, no orgasms – the black bean overrules the white.
-
White + White\ "Lucky draw… but denial is optional."
-
Freedom to indulge, though I often choose self-denial anyway. Examples:
-
Edge for 30 minutes, then ask permission to climax (50% chance).
-
Use toys freely, but end the session frustrated.
-
The Dynamic Ratio Twist:
-
The starting 10:10 ratio isn’t fixed. Adjust it based on behavior:
-
Good deeds? Swap a black bean for a white one.
-
Mistakes? Replace a white bean with a black one.
-
Single beans can also decide smaller stakes, like:
-
"Should this edge turn into a ruined orgasm?"
-
"Do I deserve dessert tonight?"
Why It Works:
-
Control: The beans dictate your fate, but you tweak the odds through obedience.
-
Flexibility: Use pairs for major tasks, single beans for quick decisions.
-
Psychological tease: Even "white + white" can mean denial – because you choose the rules.
-
-
 @ 472f440f:5669301e
2024-08-28 22:34:51
@ 472f440f:5669301e
2024-08-28 22:34:51nostr:note1x82zkl9knpkgk07wlhycex6una0zjscgcafzaq2pfjfq6h3tz8jqr0em9m
A lot of the problems the US is suffering from today stem from the fact that we've been managed by a political class that is economically illiterate for decades.
"Debt is only money we owe ourselves."
"We need to pass this $2 Trillion spending bill to drive down prices."
"We need to phase out reliable energy generation in favor of unreliable renewables."
"Nuclear energy is bad so we can't build anymore reactors."
"We need to bail out the banks that introduced systemic risks into our economy or the world will devolve into chaos."
"We need to lock down the economy and print trillions of dollars to pay people for staying home from work while we flatten the curve."
"A prolonged zero interest rate environment will stoke economic growth with no long-term effects."
"We need to ship all of our manufacturing over seas so that we can flood the world with dollars, make the USD the reserve currency of the world, and lower prices at home. Good middle class jobs be damned."
The list goes on and on.
The ramifications of these compounding economically illiterate policies has left the country, and the world at large, in an extremely vulnerable position. We are sitting on more than $35 TRILLION of debt on the national balance sheet with another $220 TRILLION in off balance sheet liabilities in the form of Social Security, Medicare, Medicade and other handouts the government has promised to make in the future. And, worse yet, many policies, particularly spending bills that pack in new regulations, have indirectly eroded individual freedoms.
The annual military budget increases the war machine and the military industrial complex, which then use the money they've been allocated to lobby for laws like the Patriot Act. Completely obliterating the fourth amendment in an effort to "protect the country from terrorism". I sit here and shudder at the thought of how much money has been wasted on programs like the TSA and the additional lost economic productivity that comes with people idiotically taking off their shoes and standing in a radioactive tube with their hands up while some mouth breather who couldn't guard a Pixie cup from a three year old yells at you. Let alone the potential economic activity and partnerships that are blown up with the bombs we drop using money we don't have.
The mad dash to "nEt ZeRo EmIsSiOnS" also brings along with it inflationary pressures that result in increased economic stress for the Common Man while restricting his freedoms. Nothing makes this clearer than the Orwellian "Inflation Reduction Act" that forced net zero energy transitions policies through a bill. The policies limit the options individual Americans and corporations have when it comes to utilizing the energy sources they deem most economically viable at any given point in time. An over subsidization of wind and solar and a demonization of oil, natural gas, coal and nuclear has introduced economic imbalances that are leading to a capital misallocation of epic proportions. This has, in turn, led to less reliable energy systems and overall higher energy costs.
And now the incumbent administration, now headed by Kamala Harris, is pushing for an unrealized capital gains tax that is sure to scare tens of billions of dollars worth of capital outside of the borders of the US. We touched on it when it was originally being floated last week. However, at the time it seemed like the campaign was floating a litmus test to gauge how it would be received if it became an official policy. Today it became clear that this will be an official policy if Harris gets into office and garners the necessary votes to push it through.
What's worse is the fact that one of her lead economic advisors, Bharat Rama, joined CNBC this morning to not only confirm that this is the official policy stance of the Harris campaign, but to say that people should be okay with this because they already pay an "unrealized gain tax" in the form of property taxes. Not only is it not true that property taxes are technically not unrealized gain taxes, but it's also horrible framing. Property taxes are one of the most reviled taxes that people have to pay after income taxes. No one likes paying property taxes. Especially when they look at the laughable public schooling system that they fund.
Doubling down on failed policy seems to be the modus operandi of Kamala Harris and the Marxists on her team. An unrealized gains tax is nothing more than asset confiscation by a corrupt government that has completely lost control of its finances. It will destroy the wealth of the nation. "But it will only affect people who have more than $100M. Stop talking about this, it won't affect you at all! You poor rich wannabe."
People who have attained hundreds of millions of dollars have done so because they are smart. (Most of them at least.) And they worked extremely hard to build businesses to acquire their wealth. If you think they are stupid enough to stand by and let the government swoop in and confiscate that wealth, I have a bitcoin privacy fork to sell you. They will move their money out of the country on November 6th and the Harris administration will be forced to begin lowering the threshold of who has to pay unrealized gains taxes.
$50m
$25m
$10m
$1m
$100k
They will not stop doubling down on their incompetence. These people should be laughed out of polite society and marooned on an island for floating policy as potentially dangerous to the US economy as this unrealized tax is.
This is why we bitcoin. Bitcoin gives people the ability to store their wealth in an asset that is extremely hard to confiscate if secured properly. Bitcoin gives you leverage from which to fight back against this type of overt Marxism.
Final thought... It is abnormally humid on my village by the sea for a late August day.
-
 @ 1ad9086c:7dd47af4
2025-02-08 06:31:34
@ 1ad9086c:7dd47af4
2025-02-08 06:31:34Today I'm attending an interesting event about new bitcoinsolutions for our society. I tallk with Shaun about the possibilities of Yakihonne about decentralized media. Good initiative for keeping up with all voices.
-
 @ 31da2214:af2508e2
2025-02-10 10:08:06
@ 31da2214:af2508e2
2025-02-10 10:08:06A global privacy nightmare is unfolding. The UK government secretly ordered Apple to backdoor encrypted iCloud storage worldwide—but Apple is legally forbidden from revealing this order, or they face criminal charges. This affects 2 BILLION USERS.
Here’s the full story & why it’s part of a much bigger power grab. 🧵👇 [Thread by @sayerjigmi on Thread Reader App]
1) The UK's Secret Order to Backdoor Encryption 🔓
Under the UK’s Investigatory Powers Act (IPA) 2016, Apple was served a Technical Capability Notice (TCN)—forcing them to create a backdoor for encrypted iCloud data.
This is not limited to UK users. It applies worldwide, meaning your private files are at risk, no matter where you live.
🔗 @macworld report
2) Apple’s Legal Gag Order 🤐
Apple is legally forbidden from revealing this order. If Apple even acknowledges that the UK issued this demand, they could face criminal charges.
This is a secret government order with global consequences.
3) A Global Threat to Encryption 🌍
This isn’t just about the UK (although they are leading the charge in threatening citizens in OTHER countries for violating BRITISH censorship laws!).
If Apple complies, every government in the world will demand the same access—from the US to China to authoritarian regimes.
End-to-end encryption would be effectively dead.
4) Apple’s Dilemma: Comply or Withdraw? 🚪
Apple has two choices:
- Comply & weaken encryption globally.
- Refuse & withdraw services from the UK.WhatsApp & Signal faced similar threats last year and vowed to leave the UK rather than compromise security. Will Apple do the same?
🚨 Watch the heated discussion between Damian Collins, director of CCDH (architect of the UK Online Safety Bill), and Signal’s CEO: YouTube Link
5) Why This Matters: Encryption Protects Everything 🔐
- Encryption protects financial data, health records, personal security (e.g., where you live or work), and private conversations.
- Governments always say they need backdoors for national security—but history shows they’re used for mass surveillance.
- Once a backdoor exists, hackers, rogue employees, and other governments WILL find it.
6) The UK’s War on Encryption 🛡️
The UK is trying to dominate the global surveillance & censorship landscape.
While the US, Canada, Australia, and New Zealand have supported strong encryption to mitigate cyber threats, the UK stands alone in its war on encryption.
7) The Free Speech Crackdown 🗣️
This isn’t just about encryption—it’s about control. Governments worldwide are criminalizing dissent and censoring free speech, using tech companies as their enforcement arms.
🔗 GreenMedInfo Report
8) The Global Censorship Agenda 🌐
This ties into the UK’s broader, GLOBALLY ORCHESTRATED censorship agenda:
- The Online Safety Bill criminalizes encrypted messaging & forces platforms to scan private messages.
- The Digital Services Act (EU) gives governments the power to shut down online content they don’t like.
- Leaked US-UK documents show direct coordination between UK intelligence & the Biden administration to censor online speech.
9) The Architects of Speech Policing: CCDH 🕵️♂️
The Center for Countering Digital Hate (CCDH)—a UK intelligence-backed group—has been a driving force behind global censorship.
They were caught:
- Running “black ops” to suppress RFK Jr.’s presidential campaign.
- Leading the "Kill Musk’s Twitter" directive, trying to shut down free speech on X.
- Labeling 12 private US citizens as the “Disinformation Dozen” to justify mass censorship.
🔗 Reclaim the Net Investigation
10) The Pattern is Clear: Surveillance + Censorship 🔍
1️⃣ Governments create "safety" laws to justify surveillance.
2️⃣ They pressure tech companies to enforce censorship.
3️⃣ Once encrypted services are gone, nothing is private anymore.This is the biggest attack on digital freedom in history.
11) What Can We Do? 💪
- Support companies that refuse to build backdoors (Signal, ProtonMail, etc.).
- Push for legislation that protects encryption & free speech.
- Stay informed & spread awareness—governments count on secrecy to push these policies through.
- Follow and support privacy and internet freedom organizations such as:
- @G_W_Forum
- @FFO_Freedom
- @ReclaimTheNetHQ
12) The Ultimate Power Grab: Controlling All Digital Communication 📱
If Apple caves, every other platform will be forced to follow.
📌 The UK’s Global Playbook:
- A backdoor to encryption (Investigatory Powers Act).
- A government-linked censorship network (CCDH).
- A speech-policing framework that extends worldwide (Online Safety Bill).This is a global effort to control what people can say, share, and store privately.
13) The Final Stand: Will You Comply or Resist? ⚔️🚨
They want total control—your speech, your privacy, your elections. This is the defining battle of our time.
🇬🇧 UK’s war on encryption = Global censorship blueprint.
🗳️ Election meddling + speech policing = A hijacked democracy.📢 Digital freedom is human freedom.
Stand up. Speak out. Fight back. 🏴☠️🔥
Full thread preserved by Thread Reader App.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Splitpages
The simplest possible service: it splitted PDF pages in half.
Created specially to solve the problem of those scanned books that come with two pages side-by-side as if they were a single page and are much harder to read on Kindle because of that.

It required me to learn about Heroku Buildpacks though, and fork or contribute to a Heroku Buildpack that embedded a mupdf binary.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28tempreites
My first library to get stars on GitHub, was a very stupid templating library that used just HTML and HTML attributes ("DSL-free"). I was inspired by http://microjs.com/ at the time and ended up not using the library. Probably no one ever did.
-
 @ 42342239:1d80db24
2025-02-10 08:16:32
@ 42342239:1d80db24
2025-02-10 08:16:32The risks associated with cryptocurrencies have recently received attention in the media, where e.g. the Swedish Financial Supervisory Authority warns of the high volatility and risk of investments in crypto. Within the EU, as usual, significant efforts are being made to expand the already extensive regulatory framework. Meanwhile, in the US, there has been a marked turnaround. Even the presidential family has launched their own cryptocurrencies, resulting in criticism from industry experts .
Important perspectives, however, are conspicuous by their absence in the conversation.
Iain McGilchrist, a British psychiatrist and philosopher, has introduced the hemispheric hypothesis (a theory about how the brain's two hemispheres function). The left hemisphere is more detail- and control-oriented, while the right hemisphere is more holistic. A society dominated by the left hemisphere, such as our own according to McGilchrist , "would see it as its task to control everything maximally and would have a paranoid feeling that we need to have surveillance cameras everywhere...".
During a speech at the World Economic Forum, President Trump recently stated that conservatives complain about big banks, such as Bank of America, not allowing them to conduct business within the bank. Critics argue that the American banking system has been used to persecute political opponents, both during Obama's and Biden's terms. Under Obama, 'Operation Chokepoint' was introduced to limit certain businesses' access to banking services. A subcommittee in the Senate now wants to eradicate this phenomenon.
More and more people are discovering that their money is not always under their control. Non-profit associations and congregations are not allowed to open bank accounts. Sometimes they are even thrown out as bank customers. Others may report being subjected to lengthy interrogations by the bank about what they intend to do with their money, even when they just want to transfer funds between their own accounts. Rejected churches are met with silence, while a bank account is (still!) necessary to fully operate in society.
When leading economists at the International Monetary Fund (IMF) argue that a cashless society can threaten fundamental rights , including property rights, when churches are refused bank accounts in what is described as "a threat to civil society" and when regulations still fail to combat organised crime , is it not reasonable to wonder if we are on the right path?
With cash, people can pay freely without intermediaries, which constitutes a form of financial freedom. The notes you hold in your hand are your own. Cryptocurrencies, such as Bitcoin, offer a similar possibility: an electronic, peer-to-peer cash system (person to person).
A society dominated by the left hemisphere results in a pathological need for control, according to McGilchrist. A more holistic perspective, taking into account the right hemisphere, would acknowledge that too much control can be detrimental, that property rights are a fundamental right, and that financial freedom is a human right. Do these perspectives not deserve more attention?
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28litepub
A Go library that abstracts all the burdensome ActivityPub things and provides just the right amount of helpers necessary to integrate an existing website into the "fediverse" (what an odious name). Made for the gravity integration.
See also
-
-
 @ 2cd78afb:f577f59a
2025-02-10 06:23:10
@ 2cd78afb:f577f59a
2025-02-10 06:23:10Looking for a reliable computer tech support service? Small Business IT Support offers professional solutions to maintain the functionality of your systems. Hardware troubleshooting, software installation, virus removal, network configuration, and performance optimization are among the services we offer. Whether you require remote or on-site support, our knowledgeable specialists guarantee optimum effectiveness and little downtime. You may get quick, expert, and reasonably priced IT solutions that are suited to your company's requirements with our computer tech support service. For professional assistance and smooth operations, get in touch with us right now!
-
 @ 6389be64:ef439d32
2025-01-14 01:31:12
@ 6389be64:ef439d32
2025-01-14 01:31:12Bitcoin is more than money, more than an asset, and more than a store of value. Bitcoin is a Prime Mover, an enabler and it ignites imaginations. It certainly fueled an idea in my mind. The idea integrates sensors, computational prowess, actuated machinery, power conversion, and electronic communications to form an autonomous, machined creature roaming forests and harvesting the most widespread and least energy-dense fuel source available. I call it the Forest Walker and it eats wood, and mines Bitcoin.
I know what you're thinking. Why not just put Bitcoin mining rigs where they belong: in a hosted facility sporting electricity from energy-dense fuels like natural gas, climate-controlled with excellent data piping in and out? Why go to all the trouble building a robot that digests wood creating flammable gasses fueling an engine to run a generator powering Bitcoin miners? It's all about synergy.
Bitcoin mining enables the realization of multiple, seemingly unrelated, yet useful activities. Activities considered un-profitable if not for Bitcoin as the Prime Mover. This is much more than simply mining the greatest asset ever conceived by humankind. It’s about the power of synergy, which Bitcoin plays only one of many roles. The synergy created by this system can stabilize forests' fire ecology while generating multiple income streams. That’s the realistic goal here and requires a brief history of American Forest management before continuing.
Smokey The Bear
In 1944, the Smokey Bear Wildfire Prevention Campaign began in the United States. “Only YOU can prevent forest fires” remains the refrain of the Ad Council’s longest running campaign. The Ad Council is a U.S. non-profit set up by the American Association of Advertising Agencies and the Association of National Advertisers in 1942. It would seem that the U.S. Department of the Interior was concerned about pesky forest fires and wanted them to stop. So, alongside a national policy of extreme fire suppression they enlisted the entire U.S. population to get onboard via the Ad Council and it worked. Forest fires were almost obliterated and everyone was happy, right? Wrong.
Smokey is a fantastically successful bear so forest fires became so few for so long that the fuel load - dead wood - in forests has become very heavy. So heavy that when a fire happens (and they always happen) it destroys everything in its path because the more fuel there is the hotter that fire becomes. Trees, bushes, shrubs, and all other plant life cannot escape destruction (not to mention homes and businesses). The soil microbiology doesn’t escape either as it is burned away even in deeper soils. To add insult to injury, hydrophobic waxy residues condense on the soil surface, forcing water to travel over the ground rather than through it eroding forest soils. Good job, Smokey. Well done, Sir!
Most terrestrial ecologies are “fire ecologies”. Fire is a part of these systems’ fuel load and pest management. Before we pretended to “manage” millions of acres of forest, fires raged over the world, rarely damaging forests. The fuel load was always too light to generate fires hot enough to moonscape mountainsides. Fires simply burned off the minor amounts of fuel accumulated since the fire before. The lighter heat, smoke, and other combustion gasses suppressed pests, keeping them in check and the smoke condensed into a plant growth accelerant called wood vinegar, not a waxy cap on the soil. These fires also cleared out weak undergrowth, cycled minerals, and thinned the forest canopy, allowing sunlight to penetrate to the forest floor. Without a fire’s heat, many pine tree species can’t sow their seed. The heat is required to open the cones (the seed bearing structure) of Spruce, Cypress, Sequoia, Jack Pine, Lodgepole Pine and many more. Without fire forests can’t have babies. The idea was to protect the forests, and it isn't working.
So, in a world of fire, what does an ally look like and what does it do?
Meet The Forest Walker

For the Forest Walker to work as a mobile, autonomous unit, a solid platform that can carry several hundred pounds is required. It so happens this chassis already exists but shelved.
Introducing the Legged Squad Support System (LS3). A joint project between Boston Dynamics, DARPA, and the United States Marine Corps, the quadrupedal robot is the size of a cow, can carry 400 pounds (180 kg) of equipment, negotiate challenging terrain, and operate for 24 hours before needing to refuel. Yes, it had an engine. Abandoned in 2015, the thing was too noisy for military deployment and maintenance "under fire" is never a high-quality idea. However, we can rebuild it to act as a platform for the Forest Walker; albeit with serious alterations. It would need to be bigger, probably. Carry more weight? Definitely. Maybe replace structural metal with carbon fiber and redesign much as 3D printable parts for more effective maintenance.
The original system has a top operational speed of 8 miles per hour. For our purposes, it only needs to move about as fast as a grazing ruminant. Without the hammering vibrations of galloping into battle, shocks of exploding mortars, and drunken soldiers playing "Wrangler of Steel Machines", time between failures should be much longer and the overall energy consumption much lower. The LS3 is a solid platform to build upon. Now it just needs to be pulled out of the mothballs, and completely refitted with outboard equipment.
The Small Branch Chipper

When I say “Forest fuel load” I mean the dead, carbon containing litter on the forest floor. Duff (leaves), fine-woody debris (small branches), and coarse woody debris (logs) are the fuel that feeds forest fires. Walk through any forest in the United States today and you will see quite a lot of these materials. Too much, as I have described. Some of these fuel loads can be 8 tons per acre in pine and hardwood forests and up to 16 tons per acre at active logging sites. That’s some big wood and the more that collects, the more combustible danger to the forest it represents. It also provides a technically unlimited fuel supply for the Forest Walker system.
The problem is that this detritus has to be chewed into pieces that are easily ingestible by the system for the gasification process (we’ll get to that step in a minute). What we need is a wood chipper attached to the chassis (the LS3); its “mouth”.
A small wood chipper handling material up to 2.5 - 3.0 inches (6.3 - 7.6 cm) in diameter would eliminate a substantial amount of fuel. There is no reason for Forest Walker to remove fallen trees. It wouldn’t have to in order to make a real difference. It need only identify appropriately sized branches and grab them. Once loaded into the chipper’s intake hopper for further processing, the beast can immediately look for more “food”. This is essentially kindling that would help ignite larger logs. If it’s all consumed by Forest Walker, then it’s not present to promote an aggravated conflagration.
I have glossed over an obvious question: How does Forest Walker see and identify branches and such? LiDaR (Light Detection and Ranging) attached to Forest Walker images the local area and feed those data to onboard computers for processing. Maybe AI plays a role. Maybe simple machine learning can do the trick. One thing is for certain: being able to identify a stick and cause robotic appendages to pick it up is not impossible.
Great! We now have a quadrupedal robot autonomously identifying and “eating” dead branches and other light, combustible materials. Whilst strolling through the forest, depleting future fires of combustibles, Forest Walker has already performed a major function of this system: making the forest safer. It's time to convert this low-density fuel into a high-density fuel Forest Walker can leverage. Enter the gasification process.
The Gassifier

The gasifier is the heart of the entire system; it’s where low-density fuel becomes the high-density fuel that powers the entire system. Biochar and wood vinegar are process wastes and I’ll discuss why both are powerful soil amendments in a moment, but first, what’s gasification?
Reacting shredded carbonaceous material at high temperatures in a low or no oxygen environment converts the biomass into biochar, wood vinegar, heat, and Synthesis Gas (Syngas). Syngas consists primarily of hydrogen, carbon monoxide, and methane. All of which are extremely useful fuels in a gaseous state. Part of this gas is used to heat the input biomass and keep the reaction temperature constant while the internal combustion engine that drives the generator to produce electrical power consumes the rest.
Critically, this gasification process is “continuous feed”. Forest Walker must intake biomass from the chipper, process it to fuel, and dump the waste (CO2, heat, biochar, and wood vinegar) continuously. It cannot stop. Everything about this system depends upon this continual grazing, digestion, and excretion of wastes just as a ruminal does. And, like a ruminant, all waste products enhance the local environment.
When I first heard of gasification, I didn’t believe that it was real. Running an electric generator from burning wood seemed more akin to “conspiracy fantasy” than science. Not only is gasification real, it’s ancient technology. A man named Dean Clayton first started experiments on gasification in 1699 and in 1901 gasification was used to power a vehicle. By the end of World War II, there were 500,000 Syngas powered vehicles in Germany alone because of fossil fuel rationing during the war. The global gasification market was $480 billion in 2022 and projected to be as much as $700 billion by 2030 (Vantage Market Research). Gasification technology is the best choice to power the Forest Walker because it’s self-contained and we want its waste products.
Biochar: The Waste

Biochar (AKA agricultural charcoal) is fairly simple: it’s almost pure, solid carbon that resembles charcoal. Its porous nature packs large surface areas into small, 3 dimensional nuggets. Devoid of most other chemistry, like hydrocarbons (methane) and ash (minerals), biochar is extremely lightweight. Do not confuse it with the charcoal you buy for your grill. Biochar doesn’t make good grilling charcoal because it would burn too rapidly as it does not contain the multitude of flammable components that charcoal does. Biochar has several other good use cases. Water filtration, water retention, nutrient retention, providing habitat for microscopic soil organisms, and carbon sequestration are the main ones that we are concerned with here.
Carbon has an amazing ability to adsorb (substances stick to and accumulate on the surface of an object) manifold chemistries. Water, nutrients, and pollutants tightly bind to carbon in this format. So, biochar makes a respectable filter and acts as a “battery” of water and nutrients in soils. Biochar adsorbs and holds on to seven times its weight in water. Soil containing biochar is more drought resilient than soil without it. Adsorbed nutrients, tightly sequestered alongside water, get released only as plants need them. Plants must excrete protons (H+) from their roots to disgorge water or positively charged nutrients from the biochar's surface; it's an active process.
Biochar’s surface area (where adsorption happens) can be 500 square meters per gram or more. That is 10% larger than an official NBA basketball court for every gram of biochar. Biochar’s abundant surface area builds protective habitats for soil microbes like fungi and bacteria and many are critical for the health and productivity of the soil itself.
The “carbon sequestration” component of biochar comes into play where “carbon credits” are concerned. There is a financial market for carbon. Not leveraging that market for revenue is foolish. I am climate agnostic. All I care about is that once solid carbon is inside the soil, it will stay there for thousands of years, imparting drought resiliency, fertility collection, nutrient buffering, and release for that time span. I simply want as much solid carbon in the soil because of the undeniably positive effects it has, regardless of any climactic considerations.
Wood Vinegar: More Waste

Another by-product of the gasification process is wood vinegar (Pyroligneous acid). If you have ever seen Liquid Smoke in the grocery store, then you have seen wood vinegar. Principally composed of acetic acid, acetone, and methanol wood vinegar also contains ~200 other organic compounds. It would seem intuitive that condensed, liquefied wood smoke would at least be bad for the health of all living things if not downright carcinogenic. The counter intuition wins the day, however. Wood vinegar has been used by humans for a very long time to promote digestion, bowel, and liver health; combat diarrhea and vomiting; calm peptic ulcers and regulate cholesterol levels; and a host of other benefits.
For centuries humans have annually burned off hundreds of thousands of square miles of pasture, grassland, forest, and every other conceivable terrestrial ecosystem. Why is this done? After every burn, one thing becomes obvious: the almost supernatural growth these ecosystems exhibit after the burn. How? Wood vinegar is a component of this growth. Even in open burns, smoke condenses and infiltrates the soil. That is when wood vinegar shows its quality.
This stuff beefs up not only general plant growth but seed germination as well and possesses many other qualities that are beneficial to plants. It’s a pesticide, fungicide, promotes beneficial soil microorganisms, enhances nutrient uptake, and imparts disease resistance. I am barely touching a long list of attributes here, but you want wood vinegar in your soil (alongside biochar because it adsorbs wood vinegar as well).
The Internal Combustion Engine

Conversion of grazed forage to chemical, then mechanical, and then electrical energy completes the cycle. The ICE (Internal Combustion Engine) converts the gaseous fuel output from the gasifier to mechanical energy, heat, water vapor, and CO2. It’s the mechanical energy of a rotating drive shaft that we want. That rotation drives the electric generator, which is the heartbeat we need to bring this monster to life. Luckily for us, combined internal combustion engine and generator packages are ubiquitous, delivering a defined energy output given a constant fuel input. It’s the simplest part of the system.
The obvious question here is whether the amount of syngas provided by the gasification process will provide enough energy to generate enough electrons to run the entire system or not. While I have no doubt the energy produced will run Forest Walker's main systems the question is really about the electrons left over. Will it be enough to run the Bitcoin mining aspect of the system? Everything is a budget.
CO2 Production For Growth

Plants are lollipops. No matter if it’s a tree or a bush or a shrubbery, the entire thing is mostly sugar in various formats but mostly long chain carbohydrates like lignin and cellulose. Plants need three things to make sugar: CO2, H2O and light. In a forest, where tree densities can be quite high, CO2 availability becomes a limiting growth factor. It’d be in the forest interests to have more available CO2 providing for various sugar formation providing the organism with food and structure.
An odd thing about tree leaves, the openings that allow gasses like the ever searched for CO2 are on the bottom of the leaf (these are called stomata). Not many stomata are topside. This suggests that trees and bushes have evolved to find gasses like CO2 from below, not above and this further suggests CO2 might be in higher concentrations nearer the soil.
The soil life (bacterial, fungi etc.) is constantly producing enormous amounts of CO2 and it would stay in the soil forever (eventually killing the very soil life that produces it) if not for tidal forces. Water is everywhere and whether in pools, lakes, oceans or distributed in “moist” soils water moves towards to the moon. The water in the soil and also in the water tables below the soil rise toward the surface every day. When the water rises, it expels the accumulated gasses in the soil into the atmosphere and it’s mostly CO2. It’s a good bet on how leaves developed high populations of stomata on the underside of leaves. As the water relaxes (the tide goes out) it sucks oxygenated air back into the soil to continue the functions of soil life respiration. The soil “breathes” albeit slowly.
The gasses produced by the Forest Walker’s internal combustion engine consist primarily of CO2 and H2O. Combusting sugars produce the same gasses that are needed to construct the sugars because the universe is funny like that. The Forest Walker is constantly laying down these critical construction elements right where the trees need them: close to the ground to be gobbled up by the trees.
The Branch Drones

During the last ice age, giant mammals populated North America - forests and otherwise. Mastodons, woolly mammoths, rhinos, short-faced bears, steppe bison, caribou, musk ox, giant beavers, camels, gigantic ground-dwelling sloths, glyptodons, and dire wolves were everywhere. Many were ten to fifteen feet tall. As they crashed through forests, they would effectively cleave off dead side-branches of trees, halting the spread of a ground-based fire migrating into the tree crown ("laddering") which is a death knell for a forest.
These animals are all extinct now and forests no longer have any manner of pruning services. But, if we build drones fitted with cutting implements like saws and loppers, optical cameras and AI trained to discern dead branches from living ones, these drones could effectively take over pruning services by identifying, cutting, and dropping to the forest floor, dead branches. The dropped branches simply get collected by the Forest Walker as part of its continual mission.
The drones dock on the back of the Forest Walker to recharge their batteries when low. The whole scene would look like a grazing cow with some flies bothering it. This activity breaks the link between a relatively cool ground based fire and the tree crowns and is a vital element in forest fire control.
The Bitcoin Miner

Mining is one of four monetary incentive models, making this system a possibility for development. The other three are US Dept. of the Interior, township, county, and electrical utility company easement contracts for fuel load management, global carbon credits trading, and data set sales. All the above depends on obvious questions getting answered. I will list some obvious ones, but this is not an engineering document and is not the place for spreadsheets. How much Bitcoin one Forest Walker can mine depends on everything else. What amount of biomass can we process? Will that biomass flow enough Syngas to keep the lights on? Can the chassis support enough mining ASICs and supporting infrastructure? What does that weigh and will it affect field performance? How much power can the AC generator produce?
Other questions that are more philosophical persist. Even if a single Forest Walker can only mine scant amounts of BTC per day, that pales to how much fuel material it can process into biochar. We are talking about millions upon millions of forested acres in need of fuel load management. What can a single Forest Walker do? I am not thinking in singular terms. The Forest Walker must operate as a fleet. What could 50 do? 500?
What is it worth providing a service to the world by managing forest fuel loads? Providing proof of work to the global monetary system? Seeding soil with drought and nutrient resilience by the excretion, over time, of carbon by the ton? What did the last forest fire cost?
The Mesh Network

What could be better than one bitcoin mining, carbon sequestering, forest fire squelching, soil amending behemoth? Thousands of them, but then they would need to be able to talk to each other to coordinate position, data handling, etc. Fitted with a mesh networking device, like goTenna or Meshtastic LoRa equipment enables each Forest Walker to communicate with each other.
Now we have an interconnected fleet of Forest Walkers relaying data to each other and more importantly, aggregating all of that to the last link in the chain for uplink. Well, at least Bitcoin mining data. Since block data is lightweight, transmission of these data via mesh networking in fairly close quartered environs is more than doable. So, how does data transmit to the Bitcoin Network? How do the Forest Walkers get the previous block data necessary to execute on mining?
Back To The Chain

Getting Bitcoin block data to and from the network is the last puzzle piece. The standing presumption here is that wherever a Forest Walker fleet is operating, it is NOT within cell tower range. We further presume that the nearest Walmart Wi-Fi is hours away. Enter the Blockstream Satellite or something like it.
A separate, ground-based drone will have two jobs: To stay as close to the nearest Forest Walker as it can and to provide an antennae for either terrestrial or orbital data uplink. Bitcoin-centric data is transmitted to the "uplink drone" via the mesh networked transmitters and then sent on to the uplink and the whole flow goes in the opposite direction as well; many to one and one to many.
We cannot transmit data to the Blockstream satellite, and it will be up to Blockstream and companies like it to provide uplink capabilities in the future and I don't doubt they will. Starlink you say? What’s stopping that company from filtering out block data? Nothing because it’s Starlink’s system and they could decide to censor these data. It seems we may have a problem sending and receiving Bitcoin data in back country environs.
But, then again, the utility of this system in staunching the fuel load that creates forest fires is extremely useful around forested communities and many have fiber, Wi-Fi and cell towers. These communities could be a welcoming ground zero for first deployments of the Forest Walker system by the home and business owners seeking fire repression. In the best way, Bitcoin subsidizes the safety of the communities.
Sensor Packages
LiDaR

The benefit of having a Forest Walker fleet strolling through the forest is the never ending opportunity for data gathering. A plethora of deployable sensors gathering hyper-accurate data on everything from temperature to topography is yet another revenue generator. Data is valuable and the Forest Walker could generate data sales to various government entities and private concerns.
LiDaR (Light Detection and Ranging) can map topography, perform biomass assessment, comparative soil erosion analysis, etc. It so happens that the Forest Walker’s ability to “see,” to navigate about its surroundings, is LiDaR driven and since it’s already being used, we can get double duty by harvesting that data for later use. By using a laser to send out light pulses and measuring the time it takes for the reflection of those pulses to return, very detailed data sets incrementally build up. Eventually, as enough data about a certain area becomes available, the data becomes useful and valuable.
Forestry concerns, both private and public, often use LiDaR to build 3D models of tree stands to assess the amount of harvest-able lumber in entire sections of forest. Consulting companies offering these services charge anywhere from several hundred to several thousand dollars per square kilometer for such services. A Forest Walker generating such assessments on the fly while performing its other functions is a multi-disciplinary approach to revenue generation.
pH, Soil Moisture, and Cation Exchange Sensing

The Forest Walker is quadrupedal, so there are four contact points to the soil. Why not get a pH data point for every step it takes? We can also gather soil moisture data and cation exchange capacities at unheard of densities because of sampling occurring on the fly during commission of the system’s other duties. No one is going to build a machine to do pH testing of vast tracts of forest soils, but that doesn’t make the data collected from such an endeavor valueless. Since the Forest Walker serves many functions at once, a multitude of data products can add to the return on investment component.
Weather Data

Temperature, humidity, pressure, and even data like evapotranspiration gathered at high densities on broad acre scales have untold value and because the sensors are lightweight and don’t require large power budgets, they come along for the ride at little cost. But, just like the old mantra, “gas, grass, or ass, nobody rides for free”, these sensors provide potential revenue benefits just by them being present.
I’ve touched on just a few data genres here. In fact, the question for universities, governmental bodies, and other institutions becomes, “How much will you pay us to attach your sensor payload to the Forest Walker?”
Noise Suppression

Only you can prevent Metallica filling the surrounds with 120 dB of sound. Easy enough, just turn the car stereo off. But what of a fleet of 50 Forest Walkers operating in the backcountry or near a township? 500? 5000? Each one has a wood chipper, an internal combustion engine, hydraulic pumps, actuators, and more cooling fans than you can shake a stick at. It’s a walking, screaming fire-breathing dragon operating continuously, day and night, twenty-four hours a day, three hundred sixty-five days a year. The sound will negatively affect all living things and that impacts behaviors. Serious engineering consideration and prowess must deliver a silencing blow to the major issue of noise.
It would be foolish to think that a fleet of Forest Walkers could be silent, but if not a major design consideration, then the entire idea is dead on arrival. Townships would not allow them to operate even if they solved the problem of widespread fuel load and neither would governmental entities, and rightly so. Nothing, not man nor beast, would want to be subjected to an eternal, infernal scream even if it were to end within days as the fleet moved further away after consuming what it could. Noise and heat are the only real pollutants of this system; taking noise seriously from the beginning is paramount.
Fire Safety

A “fire-breathing dragon” is not the worst description of the Forest Walker. It eats wood, combusts it at very high temperatures and excretes carbon; and it does so in an extremely flammable environment. Bad mix for one Forest Walker, worse for many. One must take extreme pains to ensure that during normal operation, a Forest Walker could fall over, walk through tinder dry brush, or get pounded into the ground by a meteorite from Krypton and it wouldn’t destroy epic swaths of trees and baby deer. I envision an ultimate test of a prototype to include dowsing it in grain alcohol while it’s wrapped up in toilet paper like a pledge at a fraternity party. If it runs for 72 hours and doesn’t set everything on fire, then maybe outside entities won’t be fearful of something that walks around forests with a constant fire in its belly.
The Wrap

How we think about what can be done with and adjacent to Bitcoin is at least as important as Bitcoin’s economic standing itself. For those who will tell me that this entire idea is without merit, I say, “OK, fine. You can come up with something, too.” What can we plug Bitcoin into that, like a battery, makes something that does not work, work? That’s the lesson I get from this entire exercise. No one was ever going to hire teams of humans to go out and "clean the forest". There's no money in that. The data collection and sales from such an endeavor might provide revenues over the break-even point but investment demands Alpha in this day and age. But, plug Bitcoin into an almost viable system and, voilà! We tip the scales to achieve lift-off.
Let’s face it, we haven’t scratched the surface of Bitcoin’s forcing function on our minds. Not because it’s Bitcoin, but because of what that invention means. The question that pushes me to approach things this way is, “what can we create that one system’s waste is another system’s feedstock?” The Forest Walker system’s only real waste is the conversion of low entropy energy (wood and syngas) into high entropy energy (heat and noise). All other output is beneficial to humanity.
Bitcoin, I believe, is the first product of a new mode of human imagination. An imagination newly forged over the past few millennia of being lied to, stolen from, distracted and otherwise mis-allocated to a black hole of the nonsensical. We are waking up.
What I have presented is not science fiction. Everything I have described here is well within the realm of possibility. The question is one of viability, at least in terms of the detritus of the old world we find ourselves departing from. This system would take a non-trivial amount of time and resources to develop. I think the system would garner extensive long-term contracts from those who have the most to lose from wildfires, the most to gain from hyperaccurate data sets, and, of course, securing the most precious asset in the world. Many may not see it that way, for they seek Alpha and are therefore blind to other possibilities. Others will see only the possibilities; of thinking in a new way, of looking at things differently, and dreaming of what comes next.
-
 @ e5272de9:a16a102f
2024-08-22 22:16:43
@ e5272de9:a16a102f
2024-08-22 22:16:43One of the highlights for me at the first day of nostriga nostriga was a panel discussion on web of trust with @Stuart Bowman, @Pip the social graph guy, @PABLOF7z, @hzrd149, and @ODELL. This to me is one of the most important topics in all of freedom tech, so I'd like to write up a few thoughts I had while they're still fresh on my mind, most of which revolve around the calculation of trust scores. Apologies if it's a bit long winded, don't seem to have the time to make it shorter.
What do we use for raw data?
There has been and on again, off again discussion during my time working in nostr over the sources of data that we should be using to calculate trust. In my mind we can think of the raw data as existing on a spectrum between two extremes. On one extreme, we have what I call proxy indicators of trust: follows, mutes, zaps, reactions, etc. People don't create this content with trust scores in mind, but we can and do use them as imperfect proxy indicators nontheless. And on the other extreme we have what I call explicit trust attestations, exemplified by the proposed NIP-77, authored by Lez, the heart and soul of which is that a fully explicit contextual trust attestation should have 3 fields: a context, a score, and a confidence. You fill in these fields, you say what you mean, and you mean what you say, leaving as little room for interpretation as possible. And then there is data that's in between these two extremes. A five star rating for a host on a couchsurfing platform or a vendor on an ecommerce site? A "superfollow" option in addition to a follow? These lie somewhere on the spectrum between proxy indicators on one end and explicit attestations of trust on the other.
During the panel today, Pablo and pippellia expressed the opinion that explicit trust attestations are not the way to go. Two reasons that I recall: first, that no one wants to put an exact number to trust; and second, that no one will update those numbers even if their assessment changes. These critiques have some merit to them. But I believe they miss the bigger picture.
The bigger picture
In the real world, there are two ways I can communicate trust: I can SHOW you, or I can TELL you. I can demonstrate trust through the actions that I take, such as following someone, or I can just straight up tell you that I trust someone in some context.
So here's the question: on nostr, which is the correct method to communicate trust? Proxy indicators, or explicit attestations? Do we SHOW or do we TELL?

My view is that we don't have to pick. We have to use all relevant and available raw data across the entire spectrum from one extreme to the other.

Each of these two options has its advantages and its disadvantages. The advantage of proxy indicators is that users issue them freely and easily, the result being that we are awash in a sea of data. The primary disadvantage of proxy indicators is that they often don't mean what we want them to mean. If Alice follows Bob, does that mean she trusts him? Maybe. Or maybe not. More often not. And what about context? Do we have any way of knowing?
So we use proxy indicators as a trust indicators because ... if it's the best or maybe even the only data we have, what else are we gonna do?
To do better, I argue that we need to give users more options when it comes to issuing explicit indicators of trust. But of course they're not going to do that without a reason. So to give them a reason, we have to figure out ahead of time how we're going to use the data once it's available. We have to know how to incorporate explicit trust indicators into our web of trust calculations. For the sake of argument, let's assume that we have a large dataset of proxy trust indicators (SHOW ME data) plus a small but nontrivial dataset with explicit trust attestations (TELL ME data). What we want to do is to pool all available relevant data together when we calculate trust scores. But how exactly do we do that? Which brings me to my next topic.
The calculation of trust scores
How are we even calculating the "web of trust scores" that we see today? Wikifreedia, Coracle, and a growing list of other clients have such scores. I wish I had seen more discussion in today's panel about HOW these calculation are performed. To the best of my knowledge, most clients use the same or a similar method: fetch my follows; fetch Bob's followers; calculate the set of users who are in both sets; and count up how many you get. Sometimes adjustments are made, usually a ding based on mutes. But usually, that's it. That's the WoT score.
I'll call this the "legacy WoT score" since it is basically the state of the art in nostr. The legacy WoT score can be a useful way to eliminate bots and bad actors. But it has a few disadvantages: it is, arguably, a bit of a popularity contest. It cannot see more than two hops away on your social graph. It's not very useful to new users who haven't yet built up their follows. And it's not clear how to use it to differentiate trust in different contexts.
It seems strange to me that so many clients use this single method to calculate WoT scores, but with relatively little discussion on the merits of this method as opposed to other methods. Or whether other methods even exist, for that matter.
Indeed, I believe there is another method to calculate trust scores that in most circumstances will turn out to be much more meaningful and useful. For the sake of this article, I will call this the "Grapevine WoT score" to distinguish it from the legacy WoT score. (Elsewhere I have used the phrase "influence score" in place of "Grapevine WoT score.")
The Grapevine method is (currently) based on follows and mutes, but calculated using a method entirely distinct from the legacy method, detailed here (where it is called simply the "influence score"). The Grapevine method has several advantages over the legacy method, but one in particular on the topic of SHOW versus TELL: the Grapevine method can take multiple distinct classes of data following distinct formats and pool them together, synthesizing and distilling them into a single Grapevine WoT score. By choosing different datasets, different scores corresponding to different contexts can be generated.
The future
So here's my prediction on how the future will play out. 1. The Grapevine method of trust score calculation is going to rely -- at first -- primarily on proxy indicators of trust (follows, mutes, zaps, reactions, etc) -- SHOW ME data -- because that’s the data that’s available to us in large quantities. 2. These contextual Grapevine scores will turn out to be surprisingly useful. 3. People will learn to game the scores by changing their behavior. 5. Consumers of trust data will gradually discover that SHOW ME data is becoming less and less reliable. 6. Authors of raw trust data will gradually learn that if they want their voices to be heard, they will need to communicate trust more explicitly. In ways that are harder to game. They will begin to move the needle ever so gradually towards TELL ME data. 7. Over time, larger datasets of TELL ME data will be available for input into Grapevine WoT scores. 8. As SHOW ME data becomes less reliable, and TELL ME data becomes more available, contextual Grapevine WoT scores will become more fine grained in terms of context and more reliable.
Of course, none of this will happen unless and until we start calculating Grapevine WoT scores and putting them to good use. To that end, several of us are working on the generation of these scores at brainSToRm. Right now, it's a slog to download the data to the browser. But we're working on improving the UX. And if you make it through the slog, you can export a NIP-51 list of the top-scoring pubkeys, minus the ones you're already following, and use them at clients like Amethyst or Coracle to generate a feed of content coming from the most highly "trusted" users whom you're not already following. A feed that is CUSTOMIZED by YOUR Grapevine.
So there you have it, my defense of explicit trust attestations.
-
 @ df478568:2a951e67
2025-02-07 22:34:11
@ df478568:2a951e67
2025-02-07 22:34:11Freedom tech is free and open-source software. It is free as in freedom. A common license in FOSS is the MIT license. It's the license behind Bitcoin, a peer-to-peer electronic cash system. Anyone is free to run this software. The same is true for the software at mempool.space. The software is free to use. I run it on my own server.
This is what I use to time-stamp my articles. You can use it to check transactions on the bitcoin time chain, but you need to trust that I'm not doing any funny business. I'm not, but keep in mind, the whole point of p2p elwctronic cash is that you don't trust. You verify.
The beauty of FOSS is: You don't need to trust me. You can triple-check the transactions you search on my mempool instance by looking at the official mempool.space website and blockchain.info...Or...You can run your own node on your own hardware, free of charge.
Of course, the hardware is not free. Neither is the actual bitcoin. The freedom is built into the software, but as the saying goes, "freedom isn't free." It took me years to learn how to run my own software on my own server and make it available on the clear net.
SearXNG

SearXNG is my favorite search engine. I don't like giving up my precious data to big tech located in the United States or China. I run my own search engine. I have noticed certain biases in Google searches. The biggest problem is ads.
Companies tend to pay for Yelp and Google reviews. I called an AC company I found from a local magazine that came in the mail. A portly man wearing an HVAC costume drove to my house in a white van. He had a great smile and even better social skills. The van had a slogan plastered on it like most tradie vans do. "Reviews Matter We have a 4.9 Review on Google." He also had his name painted on this van like a Bomber pilot from WW2. I won't dox him, but it was something like "Joe the closer."
I don't trust the omnipotenence of the Googs. I also don't trust fat men they call "the closer" to give me the best deal. The trick to saving sats is to choose the game-theory optimal way of negogiation.
In DUCY, by David Sklansky, I learned useful negotiation skills. Sklansky wrote classic poker books and applied his actuarial math brain to negotiation techniques. He said he would go to a Toyota dealer and say, "I'm shopping for a new Camry. I already have a price from dealership XYZ in a nearby city. What is your price?"
This changes the dynamic right from the starting line and gives the consumer the advantage. So I tried this based technique with the HVAC industrial complex. I got a quote from 3 people: 1. Joe "The Closer." 2. The Costco-sponsored HVAC Company 3. My SearXNG search results.
In essence, I apply the same logic I learned running a full bitcoin node. Remember how I said the decentralized nature of bitcoin allows you to triple-check your transactions? Running SearXNG allows me to triple check my search results in a similar fashion. I don't trust Google, Costco, or the magazine I get every month in the mail. I verify results with my own search engine.
My SearXNG does not track my location, but I set it to give me local results. To be honest, I have not verified this, but the code is on GitHub for everyone to see.
I don't want to be "sold" on an AC. I don't want an AC if I could avoid it, but my AC was as dead as dentacoin. Living in Southern California with a wife going through "the change" gave me no alternative.
The guy I found on SearXNG showed up in an unmarked van. He had a beard. He was not "a closer." He was an actual HVAC technician. He tried cleaning my unit made in the same year Weezer released their Blue album. He said he coukd jerry rig it to get it working for another few months, but the machine is on it's last days. He said a newer unit would also be more efficient so I asked him about the energy like a bitcoiner.
"How many kilowatt hours does it cost me to run my AC versus a new AC?"
I don't remember the exact answer, but I asked all three companies. He was the only one that new how to find out. He also happened to be the cheapest, but I would have bought a new AC from this guy even if he wasn't.
I told him I made a space heater out of a bitcoin miner. He had no idea this was possible, but he at least pretended to find it interesting. That's why I use SearXNG to find tradesmen. It's better than Yelp.
If you would like to try my instance of SearXNG, check it out.
523FeCpi9Gx4nR9NmSFIMEaYcI5Q4WmhYHPEPaEah84=To decrypt it, use the key behind the paywall at:
https://8gwifi.org/CipherFunctions.jsp
npub1marc26z8nh3xkj5rcx7ufkatvx6ueqhp5vfw9v5teq26z254renshtf3g0
Follow me on nostr.
All of my work is available under the Creative Commons 0 licence. If you would like to try my instance of Searxng and do not wish to support my work, find me on habla.news by searching my npub. You can find all of my work there(including encryption keys)free of charge.
Paywall On Substack
abdominal.savior.repaint
Will decrypt this ciphertext: 523FeCpi9Gx4nR9NmSFIMEaYcI5Q4WmhYHPEPaEah84=
Which will reveal my instance of SearXNG at
https://searxng.marc26z.com/
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28questo.email
This was a thing done in a brief period I liked the idea of "indiewebcamp", a stupid movement of people saying everybody should have their site and post their lives in it.
From the GitHub postmortem:
questo.email was a service that integrated email addresses into the indieweb ecosystem by providing email-to-note and email-to-webmention triggers, which could be used for people to comment through webmention using their email addresses, and be replied, and also for people to send messages from their sites directly to the email addresses of people they knew; Questo also worked as an IndieAuth provider that used people's email addresses and Mozilla Persona.
It was live from December 2014 through December 2015.
Here's how the home page looked:

See also
- jekmentions, another thing related to "indieweb"
-
 @ 17538dc2:71ed77c4
2025-01-13 18:17:24
@ 17538dc2:71ed77c4
2025-01-13 18:17:24Sci-Hub 2024 year end review is translated to English by Kagi Translate from Russian. Original text can be found in Sci-Hub's telegram channel https://t.me/freescience.
RESULTS OF 2024
First. The project received donations totaling 2 million dollars in meme coins.
The project is actively used by many students in China, which is why a group of Sci-Hub fans has emerged there. As far as I understand, the organizer of the group is actively interested in the topic of cryptocurrencies (even wrote a book). Somewhere in mid-November, the Chinese launched a meme coin in honor of the Sci-Hub project. At its peak, the coin's price reached 5 cents, and now it is somewhere around 1-2 cents. This means that the exchange rate of the Sci-Hub cryptocurrency is now almost equal to the ruble exchange rate (100 to one or so).
In general, I converted part of these donations into normal, traditional cryptocurrency (like Bitcoin) and paid for servers several months in advance. The other part is still sitting in meme coins—I hope that the token will still grow in price (there is a promotion plan). Of course, this is risky, but Sci-Hub is a project that is not afraid of risk. Therefore, anyone who wants to invest in Sci-Hub by purchasing this token can do so here: www.coingecko.com/en/coins/sci-hub
Second. A dissertation on the topic of open scientific knowledge has been defended at the Institute of Philosophy.
For those interested in the history and philosophy of science, I defended a dissertation in April at the Institute of Philosophy on the topic that scientific knowledge should be open (otherwise, it is strange to call it scientific at all). The work shows that open communication is one of the basic traditional values of science when considering science as a social institution. In other words, journals that charge for access to scientific articles are a kind of 'non-traditional orientation journals.'
Moreover, openness is an important prerequisite for rationality. Rationality is not limited to the criterion of falsification (hello Popper); it is a much more complex concept.
You can familiarize yourself with the text of the dissertation here: web.archive.org/web/20240425100014/https://iphras.ru/page26414303.htm (I provide the link through the web archive because the Institute's website, strangely enough, is glitching again at the time of writing this post).
All criticism and comments (as well as praise) regarding the dissertation can be sent to my email.
Third. Work has begun on a new declaration of open access to scientific knowledge.
Currently, all discussions on the topic of open science are conducted within the frameworks defined by the so-called BBB declarations back in 2001-2003. Within these frameworks, two main types of open access are recognized: gold, meaning open journals with an author-pays model, and green, which refers to repositories like the well-known arXiv. We can also add the so-called diamond open access, which includes open journals that are free for both authors and readers.
However, since 2003, internet technologies have advanced significantly. Today, we can already talk about such types of open access as blue (through academic social networks) or red (your beloved Sci-Hub). It is time to adopt a new declaration of open access to scientific knowledge that corresponds to the current state of scientific and technological progress.
A preliminary version of the declaration can be read and signed here: open.science.do
We will be more actively engaged in this in the coming year. Signing the declaration is an important step towards recognizing access to scientific knowledge through sites like Sci-Hub or Libgen as completely legal and ceasing to pursue them—first in the former USSR, and then in all countries of the world.
Fourth. In 2024, about one billion articles were downloaded through Sci-Hub. Despite the fact that this is unfiltered statistics, the fact remains: the popularity of the project has not decreased but only grown, despite the fact that Sci-Hub has not been updated for quite a long time. Of course, this does not mean that the site will not be updated at all now—just that the patient is more alive than dead (no matter how much some haters might wish otherwise).
The cause of open access to scientific knowledge will definitely prevail—because good always triumphs over evil.
In the new year, I wish all scientists new discoveries and large grants. Happy New Year, comrades!
-
 @ 16d11430:61640947
2025-02-10 02:35:17
@ 16d11430:61640947
2025-02-10 02:35:17The gap in mathematics that allows for free agency—the space where choice, unpredictability, and autonomy emerge—exists at the intersection of incompleteness, chaos, probability, and quantum uncertainty. These gaps create fundamental limits on determinism, leaving room for agency to exist.
- Gödel’s Incompleteness Theorems: The Limits of Formal Systems
Gödel’s theorems prove that within any sufficiently powerful mathematical system:
There exist truths that cannot be proven within that system.
The system cannot prove its own consistency.
This means that even in a world governed by mathematical laws, there are undecidable truths—facts beyond algorithmic computation. If reality is mathematical at its core, this suggests a built-in freedom: not everything is determinable from within the system.
- Chaos Theory: The Sensitivity to Initial Conditions
Chaotic systems, such as weather patterns and neural activity, exhibit extreme sensitivity to initial conditions.
Even if deterministic, they are practically unpredictable beyond a certain point.
Small choices or quantum fluctuations at the micro-level can have macroscopic consequences.
This injects a level of unpredictability into reality, making strict determinism impossible in complex systems.
- Probability & Bayesian Decision Theory: Rational Agency Within Uncertainty
In the realm of decision-making and game theory:
Bayesian inference shows how rational agents update beliefs in the face of uncertainty.
Statistical mechanics, despite governing collective behaviors, leaves space for individual unpredictability.
Nash equilibria in game theory illustrate how multiple choices can be rationally justified, allowing for strategic freedom.
Thus, within mathematical decision models, choice emerges not from randomness but from incomplete knowledge and competing optimal strategies.
- Quantum Mechanics: The Fundamental Indeterminacy of Reality
At the quantum level, Heisenberg’s Uncertainty Principle and the probabilistic nature of wavefunction collapse introduce a non-deterministic reality:
Superposition suggests that multiple possibilities coexist until measured.
Quantum entanglement links particles across vast distances, but their states are not pre-determined before observation.
The Born rule in quantum mechanics assigns probabilities rather than certainties to outcomes.
If the fundamental fabric of reality is non-deterministic, then the idea of strict mechanistic determinism collapses, opening the door to true agency.
- Computability and the Halting Problem: The Unsolvability of Certain Decisions
Turing’s Halting Problem proves that for some problems, no algorithm can determine in advance whether a computation will finish or run forever.
If reality includes such non-computable elements, then some choices are beyond pre-determined algorithmic resolution.
Human cognition, if partially non-computable, could transcend deterministic rules.
Conclusion: The Gap Between Necessity and Choice
Free agency exists in the mathematical gaps—the undecidability of logic, the unpredictability of chaos, the probabilistic nature of quantum mechanics, and the non-computability of certain decisions. These fundamental limits on strict determinism create an open space where choices emerge, allowing for freedom within a mathematically structured universe.
Thus, in the grand equation of existence, there remains an undefined variable: the will of the agent.
