-
 @ dd664d5e:5633d319
2024-06-21 19:11:51
@ dd664d5e:5633d319
2024-06-21 19:11:51Finding Catholics and Catholic-friendly content on Nostr
Obvious Catholics being obvious
nostr:npub1m4ny6hjqzepn4rxknuq94c2gpqzr29ufkkw7ttcxyak7v43n6vvsajc2jl
nostr:npub1k92qsr95jcumkpu6dffurkvwwycwa2euvx4fthv78ru7gqqz0nrs2ngfwd
nostr:npub1wqfzz2p880wq0tumuae9lfwyhs8uz35xd0kr34zrvrwyh3kvrzuskcqsyn
nostr:npub1ecdlntvjzexlyfale2egzvvncc8tgqsaxkl5hw7xlgjv2cxs705s9qs735
nostr:npub1rcr8h76csgzhdhea4a7tq5w5gydcpg9clgf0cffu6z45rnc6yp5sj7cfuz
nostr:npub1fyd0awkakq4aap70ual7mtlszjle9krffgwnsrkyua2frzmysd8qjj8gvg
nostr:npub1q0fe26apcqeeyqnlre29fqu7ysx0ucm5ly637md3zlvy2xcfsm3s0lsv4r
nostr:npub1dvdcmtp5llrp63jdlmhspe9gffsyu9ew7cu3ld3f9y7k79nxzjxqf4d4rm
nostr:npub1paxyej8f8fh57ny0fr5w2mzp9can9nkcmeu5jaerv68mhrah7t8s795ky6
nostr:npub1tvw3h5xqnuc2aq5zelxp3dy58sz7x9u8e6enkxywmrz70cg2j2zqjes44n
nostr:npub13tahtl9pjw9u5ycruqk84k6sfmkyljsr7y2pc4s840ctlm73fxeq3j6e08
nostr:npub1w4jkwspqn9svwnlrw0nfg0u2yx4cj6yfmp53ya4xp7r24k7gly4qaq30zp
Other good Christian follows
nostr:npub1hqy4zwnvsdmlml4tpgp0kgrruxamfcwpgm4g3q2tr3d2ut3kuxusx73psm
nostr:npub1cpstx8lzhwctunfe80rugz5qsj9ztw8surec9j6mf8phha68dj6qhm8j5e
nostr:npub1ak5kewf6anwkrt0qc8ua907ljkn7wm83e2ycyrpcumjvaf2upszs8r0gwg
nostr:npub1mt8x8vqvgtnwq97sphgep2fjswrqqtl4j7uyr667lyw7fuwwsjgs5mm7cz
nostr:npub1q6ya7kz84rfnw6yjmg5kyttuplwpauv43a9ug3cajztx4g0v48eqhtt3sh
nostr:npub1356t6fpjysx9vdchfg7mryv83w4pcye6a3eeke9zvsje7s2tuv4s4k805u
nostr:npub1kun5628raxpm7usdkj62z2337hr77f3ryrg9cf0vjpyf4jvk9r9smv3lhe
nostr:npub1qf6gsfapq94rj0rcptkpm9sergacmuwrjlgfx5gznjajtvkcx3psfhx6k5
nostr:npub1ll99fcrclkvgff696u8tq9vupw9fulfc8fysdf6gfwp7hassrh2sktxszt
nostr:npub1zy37ecnhpvx4lmxh4spd0898sxdj0ag8m64s9yq499zaxlg7qrqq8c53q6
nostr:npub1rtlqca8r6auyaw5n5h3l5422dm4sry5dzfee4696fqe8s6qgudks7djtfs
nostr:npub1jlrs53pkdfjnts29kveljul2sm0actt6n8dxrrzqcersttvcuv3qdjynqn
nostr:npub18zqmath26txwfhc70af8axk7pftjre9x7cf0lxkg92nvj2cpfgts8va790
Christian follow list
An exhaustive list of Christians is maintained by nostr:npub1mt8x8vqvgtnwq97sphgep2fjswrqqtl4j7uyr667lyw7fuwwsjgs5mm7cz. Just look at his list on https://listr.lol/
Catholic community
You can also join the community, to reach other catholics (usable on #Nostrudel #Coracle #Amethyst and #Satellite): nostr:naddr1qvzqqqyx7cpzqqnd3dl8hnptg9agfugwmdcmgfl7wcrfjpgfpv28ksq6dnmqc0e8qqyyxct5dphkc6trmu6k9l
Christian topic relay
And always make sure to use the #catholic hashtag, to get onto the top-specific christpill relay (add it to your relay list: wss://christpill.nostr1.com/).
Hope that helps! 😊
-
 @ 0a9436f8:9935ad4f
2024-12-12 00:10:17
@ 0a9436f8:9935ad4f
2024-12-12 00:10:17Introduction
1. The Industrial Revolution and its consequences have been a disaster for the human race. They have greatly increased the life-expectancy of those of us who live in "advanced" countries, but they have destabilized society, have made life unfulfilling, have subjected human beings to indignities, have led to widespread psychological suffering (in the Third World to physical suffering as well) and have inflicted severe damage on the natural world. The continued development of technology will worsen the situation. It will certainly subject human beings to greater indignities and inflict greater damage on the natural world, it will probably lead to greater social disruption and psychological suffering, and it may lead to increased physical suffering even in "advanced" countries.
2. The industrial-technological system may survive or it may break down. If it survives, it MAY eventually achieve a low level of physical and psychological suffering, but only after passing through a long and very painful period of adjustment and only at the cost of permanently reducing human beings and many other living organisms to engineered products and mere cogs in the social machine. Furthermore, if the system survives, the consequences will be inevitable: There is no way of reforming or modifying the system so as to prevent it from depriving people of dignity and autonomy.
3. If the system breaks down the consequences will still be very painful. But the bigger the system grows the more disastrous the results of its breakdown will be, so if it is to break down it had best break down sooner rather than later.
4. We therefore advocate a revolution against the industrial system. This revolution may or may not make use of violence; it may be sudden or it may be a relatively gradual process spanning a few decades. We can't predict any of that. But we do outline in a very general way the measures that those who hate the industrial system should take in order to prepare the way for a revolution against that form of society. This is not to be a POLITICAL revolution. Its object will be to overthrow not governments but the economic and technological basis of the present society.
5. In this article we give attention to only some of the negative developments that have grown out of the industrial-technological system. Other such developments we mention only briefly or ignore altogether. This does not mean that we regard these other developments as unimportant. For practical reasons we have to confine our discussion to areas that have received insufficient public attention or in which we have something new to say. For example, since there are well-developed environmental and wilderness movements, we have written very little about environmental degradation or the destruction of wild nature, even though we consider these to be highly important.
THE PSYCHOLOGY OF MODERN LEFTISM
6. Almost everyone will agree that we live in a deeply troubled society. One of the most widespread manifestations of the craziness of our world is leftism, so a discussion of the psychology of leftism can serve as an introduction to the discussion of the problems of modern society in general.
7. But what is leftism? During the first half of the 20th century leftism could have been practically identified with socialism. Today the movement is fragmented and it is not clear who can properly be called a leftist. When we speak of leftists in this article we have in mind mainly socialists, collectivists, "politically correct" types, feminists, gay and disability activists, animal rights activists and the like. But not everyone who is associated with one of these movements is a leftist. What we are trying to get at in discussing leftism is not so much movement or an ideology as a psychological type, or rather a collection of related types. Thus, what we mean by "leftism" will emerge more clearly in the course of our discussion of leftist psychology. (Also, see paragraphs 227-230.)
8. Even so, our conception of leftism will remain a good deal less clear than we would wish, but there doesn't seem to be any remedy for this. All we are trying to do here is indicate in a rough and approximate way the two psychological tendencies that we believe are the main driving force of modern leftism. We by no means claim to be telling the WHOLE truth about leftist psychology. Also, our discussion is meant to apply to modern leftism only. We leave open the question of the extent to which our discussion could be applied to the leftists of the 19th and early 20th centuries.
9. The two psychological tendencies that underlie modern leftism we call "feelings of inferiority" and "oversocialization." Feelings of inferiority are characteristic of modern leftism as a whole, while oversocialization is characteristic only of a certain segment of modern leftism; but this segment is highly influential.
FEELINGS OF INFERIORITY
10. By "feelings of inferiority" we mean not only inferiority feelings in the strict sense but a whole spectrum of related traits; low self-esteem, feelings of powerlessness, depressive tendencies, defeatism, guilt, self-hatred, etc. We argue that modern leftists tend to have some such feelings (possibly more or less repressed) and that these feelings are decisive in determining the direction of modern leftism.
11. When someone interprets as derogatory almost anything that is said about him (or about groups with whom he identifies) we conclude that he has inferiority feelings or low self-esteem. This tendency is pronounced among minority rights activists, whether or not they belong to the minority groups whose rights they defend. They are hypersensitive about the words used to designate minorities and about anything that is said concerning minorities. The terms "negro," "oriental," "handicapped" or "chick" for an African, an Asian, a disabled person or a woman originally had no derogatory connotation. "Broad" and "chick" were merely the feminine equivalents of "guy," "dude" or "fellow." The negative connotations have been attached to these terms by the activists themselves. Some animal rights activists have gone so far as to reject the word "pet" and insist on its replacement by "animal companion." Leftish anthropologists go to great lengths to avoid saying anything about primitive peoples that could conceivably be interpreted as negative. They want to replace the world "primitive" by "nonliterate." They seem almost paranoid about anything that might suggest that any primitive culture is inferior to our own. (We do not mean to imply that primitive cultures ARE inferior to ours. We merely point out the hypersensitivity of leftish anthropologists.)
12. Those who are most sensitive about "politically incorrect" terminology are not the average black ghetto-dweller, Asian immigrant, abused woman or disabled person, but a minority of activists, many of whom do not even belong to any "oppressed" group but come from privileged strata of society. Political correctness has its stronghold among university professors, who have secure employment with comfortable salaries, and the majority of whom are heterosexual white males from middle- to upper-middle-class families.
13. Many leftists have an intense identification with the problems of groups that have an image of being weak (women), defeated (American Indians), repellent (homosexuals) or otherwise inferior. The leftists themselves feel that these groups are inferior. They would never admit to themselves that they have such feelings, but it is precisely because they do see these groups as inferior that they identify with their problems. (We do not mean to suggest that women, Indians, etc. ARE inferior; we are only making a point about leftist psychology.)
14. Feminists are desperately anxious to prove that women are as strong and as capable as men. Clearly they are nagged by a fear that women may NOT be as strong and as capable as men.
15. Leftists tend to hate anything that has an image of being strong, good and successful. They hate America, they hate Western civilization, they hate white males, they hate rationality. The reasons that leftists give for hating the West, etc. clearly do not correspond with their real motives. They SAY they hate the West because it is warlike, imperialistic, sexist, ethnocentric and so forth, but where these same faults appear in socialist countries or in primitive cultures, the leftist finds excuses for them, or at best he GRUDGINGLY admits that they exist; whereas he ENTHUSIASTICALLY points out (and often greatly exaggerates) these faults where they appear in Western civilization. Thus it is clear that these faults are not the leftist's real motive for hating America and the West. He hates America and the West because they are strong and successful.
16. Words like "self-confidence," "self-reliance," "initiative," "enterprise," "optimism," etc., play little role in the liberal and leftist vocabulary. The leftist is anti-individualistic, pro-collectivist. He wants society to solve everyone's problems for them, satisfy everyone's needs for them, take care of them. He is not the sort of person who has an inner sense of confidence in his ability to solve his own problems and satisfy his own needs. The leftist is antagonistic to the concept of competition because, deep inside, he feels like a loser.
17. Art forms that appeal to modern leftish intellectuals tend to focus on sordidness, defeat and despair, or else they take an orgiastic tone, throwing off rational control as if there were no hope of accomplishing anything through rational calculation and all that was left was to immerse oneself in the sensations of the moment.
18. Modern leftish philosophers tend to dismiss reason, science, objective reality and to insist that everything is culturally relative. It is true that one can ask serious questions about the foundations of scientific knowledge and about how, if at all, the concept of objective reality can be defined. But it is obvious that modern leftish philosophers are not simply cool-headed logicians systematically analyzing the foundations of knowledge. They are deeply involved emotionally in their attack on truth and reality. They attack these concepts because of their own psychological needs. For one thing, their attack is an outlet for hostility, and, to the extent that it is successful, it satisfies the drive for power. More importantly, the leftist hates science and rationality because they classify certain beliefs as true (i.e., successful, superior) and other beliefs as false (i.e., failed, inferior). The leftist's feelings of inferiority run so deep that he cannot tolerate any classification of some things as successful or superior and other things as failed or inferior. This also underlies the rejection by many leftists of the concept of mental illness and of the utility of IQ tests. Leftists are antagonistic to genetic explanations of human abilities or behavior because such explanations tend to make some persons appear superior or inferior to others. Leftists prefer to give society the credit or blame for an individual's ability or lack of it. Thus if a person is "inferior" it is not his fault, but society's, because he has not been brought up properly.
19. The leftist is not typically the kind of person whose feelings of inferiority make him a braggart, an egotist, a bully, a self-promoter, a ruthless competitor. This kind of person has not wholly lost faith in himself. He has a deficit in his sense of power and self-worth, but he can still conceive of himself as having the capacity to be strong, and his efforts to make himself strong produce his unpleasant behavior. [1] But the leftist is too far gone for that. Hisfeelings of inferiority are so ingrained that he cannot conceive of himself as individually strong and valuable. Hence the collectivism of the leftist. He can feel strong only as a member of a large organization or a mass movement with which he identifies himself.
20. Notice the masochistic tendency of leftist tactics. Leftists protest by lying down in front of vehicles, they intentionally provoke police or racists to abuse them, etc. These tactics may often be effective, but many leftists use them not as a means to an end but because they PREFER masochistic tactics. Self-hatred is a leftist trait.
21. Leftists may claim that their activism is motivated by compassion or by moral principles, and moral principle does play a role for the leftist of the oversocialized type. But compassion and moral principle cannot be the main motives for leftist activism. Hostility is too prominent a component of leftist behavior; so is the drive for power. Moreover, much leftist behavior is not rationally calculated to be of benefit to the people whom the leftists claim to be trying to help. For example, if one believes that affirmative action is good for black people, does it make sense to demand affirmative action in hostile or dogmatic terms? Obviously it would be more productive to take a diplomatic and conciliatory approach that would make at least verbal and symbolic concessions to white people who think that affirmative action discriminates against them. But leftist activists do not take such an approach because it would not satisfy their emotional needs. Helping black people is not their real goal. Instead, race problems serve as an excuse for them to express their own hostility and frustrated need for power. In doing so they actually harm black people, because the activists' hostile attitude toward the white majority tends to intensify race hatred.
22. If our society had no social problems at all, the leftists would have to INVENT problems in order to provide themselves with an excuse for making a fuss.
23. We emphasize that the foregoing does not pretend to be an accurate description of everyone who might be considered a leftist. It is only a rough indication of a general tendency of leftism.
OVERSOCIALIZATION
24. Psychologists use the term "socialization" to designate the process by which children are trained to think and act as society demands. A person is said to be well socialized if he believes in and obeys the moral code of his society and fits in well as a functioning part of that society. It may seem senseless to say that many leftists are oversocialized, since the leftist is perceived as a rebel. Nevertheless, the position can be defended. Many leftists are not such rebels as they seem.
25. The moral code of our society is so demanding that no one can think, feel and act in a completely moral way. For example, we are not supposed to hate anyone, yet almost everyone hates somebody at some time or other, whether he admits it to himself or not. Some people are so highly socialized that the attempt to think, feel and act morally imposes a severe burden on them. In order to avoid feelings of guilt, they continually have to deceive themselves about their own motives and find moral explanations for feelings and actions that in reality have a non-moral origin. We use the term "oversocialized" to describe such people. [2]
26. Oversocialization can lead to low self-esteem, a sense of powerlessness, defeatism, guilt, etc. One of the most important means by which our society socializes children is by making them feel ashamed of behavior or speech that is contrary to society's expectations. If this is overdone, or if a particular child is especially susceptible to such feelings, he ends by feeling ashamed of HIMSELF. Moreover the thought and the behavior of the oversocialized person are more restricted by society's expectations than are those of the lightly socialized person. The majority of people engage in a significant amount of naughty behavior. They lie, they commit petty thefts, they break traffic laws, they goofoff at work, they hate someone, they say spiteful things or they use some underhanded trick to get ahead of the other guy. The oversocialized person cannot do these things, or if he does do them he generates in himself a sense of shame and self-hatred. The oversocialized person cannot even experience, without guilt, thoughts or feelings that are contrary to the accepted morality; he cannot think "unclean" thoughts. And socialization is not just a matter of morality; we are socialized to conform to many norms of behavior that do not fall under the heading of morality. Thus the oversocialized person is kept on a psychological leash and spends his life running on rails that society has laid down for him. In many oversocialized people this results in a sense of constraint and powerlessness that can be a severe hardship. We suggest that oversocialization is among the more serious cruelties that human beings inflict on one another.
27. We argue that a very important and influential segment of the modern left is oversocialized and that their oversocialization is of great importance in determining the direction of modern leftism. Leftists of the oversocialized type tend to be intellectuals or members of the upper-middle class. Notice that university intellectuals [3] constitute the most highly socialized segment of our society and also the most left-wing segment.
28. The leftist of the oversocialized type tries to get off his psychological leash and assert his autonomy by rebelling. But usually he is not strong enough to rebel against the most basic values of society. Generally speaking, the goals of today's leftists are NOT in conflict with the accepted morality. On the contrary, the left takes an accepted moral principle, adopts it as its own, and then accuses mainstream society of violating that principle. Examples: racial equality, equality of the sexes, helping poor people, peace as opposed to war, nonviolence generally, freedom of expression, kindness to animals. More fundamentally, the duty of the individual to serve society and the duty of society to take care of the individual. All these have been deeply rooted values of our society (or at least of its middle and upper classes [4] for a long time. These values are explicitly or implicitly expressed or presupposed in most of the material presented to us by the mainstream communications media and the educational system. Leftists, especially those of the oversocialized type, usually do not rebel against these principles but justify their hostility to society by claiming (with some degree of truth) that society is not living up to these principles.
29. Here is an illustration of the way in which the oversocialized leftist shows his real attachment to the conventional attitudes of our society while pretending to be in rebellion against it. Many leftists push for affirmative action, for moving black people into high-prestige jobs, for improved education in black schools and more money for such schools; the way of life of the black "underclass" they regard as a social disgrace. They want to integrate the black man into the system, make him a business executive, a lawyer, a scientist just like upper-middle-class white people. The leftists will reply that the last thing they want is to make the black man into a copy of the white man; instead, they want to preserve African American culture. But in what does this preservation of African American culture consist? It can hardly consist in anything more than eating black-style food, listening to black-style music, wearing black-style clothing and going to a black-style church or mosque. In other words, it can express itself only in superficial matters. In all ESSENTIAL respects most leftists of the oversocialized type want to make the black man conform to white, middle-class ideals. They want to make him study technical subjects, become an executive or a scientist, spend his life climbing the status ladder to prove that black people are as good as white. They want to make black fathers "responsible," they want black gangs to become nonviolent, etc. But these are exactly the values of the industrial-technological system. The system couldn't care less what kind of music a man listens to, what kind of clothes he wears or what religion he believes in as long as he studies in school, holds a respectable job, climbs the status ladder, is a "responsible" parent, is nonviolent and so forth. In effect, however much he may deny it, the oversocialized leftist wants to integrate the black man into the system and make him adopt its values.
30. We certainly do not claim that leftists, even of the oversocialized type, NEVER rebel against the fundamental values of our society. Clearly they sometimes do. Some oversocialized leftists have gone so far as to rebel against one of modern society's most important principles by engaging in physical violence. By their own account, violence is for them a form of "liberation." In other words, by committing violence they break through the psychological restraints that have been trained into them. Because they are oversocialized these restraints have been more confining for them than for others; hence their need to break free of them. But they usually justify their rebellion in terms of mainstream values. If they engage in violence they claim to be fighting against racism or the like.
31. We realize that many objections could be raised to the foregoing thumbnail sketch of leftist psychology. The real situation is complex, and anything like a complete description of it would take several volumes even if the necessary data were available. We claim only to have indicated very roughly the two most important tendencies in the psychology of modern leftism.
32. The problems of the leftist are indicative of the problems of our society as a whole. Low self-esteem, depressive tendencies and defeatism are not restricted to the left. Though they are especially noticeable in the left, they are widespread in our society. And today's society tries to socialize us to a greater extent than any previous society. We are even told by experts how to eat, how to exercise, how to make love, how to raise our kids and so forth.
THE POWER PROCESS
33. Human beings have a need (probably based in biology) for something that we will call the "power process." This is closely related to the need for power (which is widely recognized) but is not quite the same thing. The power process has four elements. The three most clear-cut of these we call goal, effort and attainment of goal. (Everyone needs to have goals whose attainment requires effort, and needs to succeed in attaining at least some of his goals.) The fourth element is more difficult to define and may not be necessary for everyone. We call it autonomy and will discuss it later (paragraphs 42-44).
34. Consider the hypothetical case of a man who can have anything he wants just by wishing for it. Such a man has power, but he will develop serious psychological problems. At first he will have a lot of fun, but by and by he will become acutely bored and demoralized. Eventually he may become clinically depressed. History shows that leisured aristocracies tend to become decadent. This is not true of fighting aristocracies that have to struggle to maintain their power. But leisured, secure aristocracies that have no need to exert themselves usually become bored, hedonistic and demoralized, even though they have power. This shows that power is not enough. One must have goals toward which to exercise one's power.
35. Everyone has goals; if nothing else, to obtain the physical necessities of life: food, water and whatever clothing and shelter are made necessary by the climate. But the leisured aristocrat obtains these things without effort. Hence his boredom and demoralization.
36. Nonattainment of important goals results in death if the goals are physical necessities, and in frustration if nonattainment of the goals is compatible with survival. Consistent failure to attain goals throughout life results in defeatism, low self-esteem or depression.
37, Thus, in order to avoid serious psychological problems, a human being needs goals whose attainment requires effort, and he must have a reasonable rate of success in attaining his goals.
SURROGATE ACTIVITIES
38. But not every leisured aristocrat becomes bored and demoralized. For example, the emperor Hirohito, instead of sinking into decadent hedonism, devoted himself to marine biology, a field in which he became distinguished. When people do not have to exert themselves to satisfy their physical needs they often set up artificial goals for themselves. In many cases they then pursue these goals with the same energy and emotional involvement that they otherwise would have put into the search for physical necessities. Thus the aristocrats of the Roman Empire had their literary pretensions; many European aristocrats a few centuries ago invested tremendous time and energy in hunting, though they certainly didn't need the meat; other aristocracies have competed for status through elaborate displays of wealth; and a few aristocrats, like Hirohito, have turned to science.
39. We use the term "surrogate activity" to designate an activity that is directed toward an artificial goal that people set up for themselves merely in order to have some goal to work toward, or let us say, merely for the sake of the "fulfillment" that they get from pursuing the goal. Here is a rule of thumb for the identification of surrogate activities. Given a person who devotes much time and energy to the pursuit of goal X, ask yourself this: If he had to devote most of his time and energy to satisfying his biological needs, and if that effort required him to use his physical and mental faculties in a varied and interesting way, would he feel seriously deprived because he did not attain goal X? If the answer is no, then the person's pursuit of goal X is a surrogate activity. Hirohito's studies in marine biology clearly constituted a surrogate activity, since it is pretty certain that if Hirohito had had to spend his time working at interesting non-scientific tasks in order to obtain the necessities of life, he would not have felt deprived because he didn't know all about the anatomy and life-cycles of marine animals. On the other hand the pursuit of sex and love (for example) is not a surrogate activity, because most people, even if their existence were otherwise satisfactory, would feel deprived if they passed their lives without ever having a relationship with a member of the opposite sex. (But pursuit of an excessive amount of sex, more than one really needs, can be a surrogate activity.)
40. In modern industrial society only minimal effort is necessary to satisfy one's physical needs. It is enough to go through a training program to acquire some petty technical skill, then come to work on time and exert the very modest effort needed to hold a job. The only requirements are a moderate amount of intelligence and, most of all, simple OBEDIENCE. If one has those, society takes care of one from cradle to grave. (Yes, there is an underclass that cannot take the physical necessities for granted, but we are speaking here of mainstream society.) Thus it is not surprising that modern society is full of surrogate activities. These include scientific work, athletic achievement, humanitarian work, artistic and literary creation, climbing the corporate ladder, acquisition of money and material goods far beyond the point at which they cease to give any additional physical satisfaction, and social activism when it addresses issues that are not important for the activist personally, as in the case of white activists who work for the rights of nonwhite minorities. These are not always PURE surrogate activities, since for many people they may be motivated in part by needs other than the need to have some goal to pursue. Scientific work may be motivated in part by a drive for prestige, artistic creation by a need to express feelings, militant social activism by hostility. But for most people who pursue them, these activities are in large part surrogate activities. For example, the majority of scientists will probably agree that the "fulfillment" they get from their work is more important than the money and prestige they earn.
41. For many if not most people, surrogate activities are less satisfying than the pursuit of real goals (that is, goals that people would want to attain even if their need for the power process were already fulfilled). One indication of this is the fact that, in many or most cases, people who are deeply involved in surrogate activities are never satisfied, never at rest. Thus the money-maker constantly strives for more and more wealth. The scientist no sooner solves one problem than he moves on to the next. The long-distance runner drives himself to run always farther and faster. Many people who pursue surrogate activities will say that they get far more fulfillment from these activities than they do from the "mundane" business of satisfying their biological needs, but that is because in our society the effort needed to satisfy the biological needs has been reduced to triviality. More importantly, in our society people do not satisfy their biological needs AUTONOMOUSLY but by functioning as parts of an immense social machine. In contrast, people generally have a great deal of autonomy in pursuing their surrogate activities.
AUTONOMY
42. Autonomy as a part of the power process may not be necessary for every individual. But most people need a greater or lesser degree of autonomy in working toward their goals. Their efforts must be undertaken on their own initiative and must be under their own direction and control. Yet most people do not have to exert this initiative, direction and control as single individuals. It is usually enough to act as a member of a SMALL group. Thus if half a dozen people discuss a goal among themselves and make a successful joint effort to attain that goal, their need for the power process will be served. But if they work under rigid orders handed down from above that leave them no room for autonomous decision and initiative, then their need for the power process will not be served. The same is true when decisions are made on a collective basis if the group making the collective decision is so large that the role of each individual is insignificant. [5]
43. It is true that some individuals seem to have little need for autonomy. Either their drive for power is weak or they satisfy it by identifying themselves with some powerful organization to which they belong. And then there are unthinking, animal types who seem to be satisfied with a purely physical sense of power (the good combat soldier, who gets his sense of power by developing fighting skills that he is quite content to use in blind obedience to his superiors).
44. But for most people it is through the power processshaving a goal, making an AUTONOMOUS effort and attaining the goalsthat self-esteem, self-confidence and a sense of power are acquired. When one does not have adequate opportunity to go through the power process the consequences are (depending on the individual and on the way the power process is disrupted) boredom, demoralization, low self-esteem, inferiority feelings, defeatism, depression, anxiety, guilt, frustration, hostility, spouse or child abuse, insatiable hedonism, abnormal sexual behavior, sleep disorders, eating disorders, etc. [6]
SOURCES OF SOCIAL PROBLEMS
45. Any of the foregoing symptoms can occur in any society, but in modern industrial society they are present on a massive scale. We aren't the first to mention that the world today seems to be going crazy. This sort of thing is not normal for human societies. There is good reason to believe that primitive man suffered from less stress and frustration and was better satisfied with his way of life than modern man is. It is true that not all was sweetness and light in primitive societies. Abuse of women was common among the Australian aborigines, transexuality was fairly common among some of the American Indian tribes. But it does appear that GENERALLY SPEAKING the kinds of problems that we have listed in the preceding paragraph were far less common among primitive peoples than they are in modern society.
46. We attribute the social and psychological problems of modern society to the fact that that society requires people to live under conditions radically different from those under which the evolved and to behave in ways that conflict with the patterns of behavior that the human race developed while living under the earlier conditions. It is clear from what we have already written that we consider lack of opportunity to properly experience the power process as the most important of the abnormal conditions to which modern society subjects people. But it is not the only one. Before dealing with disruption of the power process as a source of social problems we will discuss some of the other sources.
47. Among the abnormal conditions present in modern industrial society are excessive density of population, isolation of man from nature, excessive rapidity of social change and the breakdown of natural small-scale communities such as the extended family, the village or the tribe.
48. It is well known that crowding increases stress and aggression. The degree of crowding that exists today and the isolation of man from nature are consequences of technological progress. All pre-industrial societies were predominantly rural. The Industrial Revolution vastly increased the size of cities and the proportion of the population that lives in them, and modern agricultural technology has made it possible for the Earth to support a far denser population than it ever did before. (Also, technology exacerbates the effects of crowding because it puts increased disruptive powers in people's hands. For example, a variety of noise-making devices: power mowers, radios, motorcycles, etc. If the use of these devices is unrestricted, people who want peace and quiet are frustrated by the noise. If their use is restricted, people who use the devices are frustrated by the regulations. But if these machines had never been invented there would have been no conflict and no frustration generated by them.)
49. For primitive societies the natural world (which usually changes only slowly) provided a stable framework and therefore a sense of security. In the modern world it is human society that dominates nature rather than the other way around, and modern society changes very rapidly owing to technological change. Thus there is no stable framework.
50. The conservatives are fools: They whine about the decay of traditional values, yet they enthusiastically support technological progress and economic growth. Apparently it never occurs to them that you can't make rapid, drastic changes in the technology and the economy of a society without causing rapid changes in all other aspects of the society as well, and that such rapid changes inevitably break down traditional values.
51. The breakdown of traditional values to some extent implies the breakdown of the bonds that hold together traditional small-scale social groups. The disintegration of small-scale social groups is also promoted by the fact that modern conditions often require or tempt individuals to move to new locations, separating themselves from their communities. Beyond that, a technological society HAS TO weaken family ties and local communities if it is to function efficiently. In modern society an individual's loyalty must be first to the system and only secondarily to a small-scale community, because if the internal loyalties of small-scale communities were stronger than loyalty to the system, such communities would pursue their own advantage at the expense of the system.
52. Suppose that a public official or a corporation executive appoints his cousin, his friend or his co-religionist to a position rather than appointing the person best qualified for the job. He has permitted personal loyalty to supersede his loyalty to the system, and that is "nepotism" or "discrimination," both of which are terrible sins in modern society. Would-be industrial societies that have done a poor job of subordinating personal or local loyalties to loyalty to the system are usually very inefficient. (Look at Latin America.) Thus an advanced industrial society can tolerate only those small-scale communities that are emasculated, tamed and made into tools of the system. [7]
53. Crowding, rapid change and the breakdown of communities have been widely recognized as sources of social problems. But we do not believe they are enough to account for the extent of the problems that are seen today.
54. A few pre-industrial cities were very large and crowded, yet their inhabitants do not seem to have suffered from psychological problems to the same extent as modern man. In America today there still are uncrowded rural areas, and we find there the same problems as in urban areas, though the problems tend to be less acute in the rural areas. Thus crowding does not seem to be the decisive factor.
55. On the growing edge of the American frontier during the 19th century, the mobility of the population probably broke down extended families and small-scale social groups to at least the same extent as these are broken down today. In fact, many nuclear families lived by choice in such isolation, having no neighbors within several miles, that they belonged to no community at all, yet they do not seem to have developed problems as a result.
56. Furthermore, change in American frontier society was very rapid and deep. A man might be born and raised in a log cabin, outside the reach of law and order and fed largely on wild meat; and by the time he arrived at old age he might be working at a regular job and living in an ordered community with effective law enforcement. This was a deeper change than that which typically occurs in the life of a modern individual, yet it does not seem to have led to psychological problems. In fact, 19th century American society had an optimistic and self-confident tone, quite unlike that of today's society. [8]
57. The difference, we argue, is that modern man has the sense (largely justified) that change is IMPOSED on him, whereas the 19th century frontiersman had the sense (also largely justified) that he created change himself, by his own choice. Thus a pioneer settled on a piece of land of his own choosing and made it into a farm through his own effort. In those days an entire county might have only a couple of hundred inhabitants and was a far more isolated and autonomous entity than a modern county is. Hence the pioneer farmer participated as a member of a relatively small group in the creation of a new, ordered community. One may well question whether the creation of this community was an improvement, but at any rate it satisfied the pioneer's need for the power process.
58. It would be possible to give other examples of societies in which there has been rapid change and/or lack of close community ties without the kind of massive behavioral aberration that is seen in today's industrial society. We contend that the most important cause of social and psychological problems in modern society is the fact that people have insufficient opportunity to go through the power process in a normal way. We don't mean to say that modern society is the only one in which the power process has been disrupted. Probably most if not all civilized societies have interfered with the power process to a greater or lesser extent. But in modern industrial society the problem has become particularly acute. Leftism, at least in its recent (mid- to late-20th century) form, is in part a symptom of deprivation with respect to the power process.
DISRUPTION OF THE POWER PROCESS IN MODERN SOCIETY
59. We divide human drives into three groups: (1) those drives that can be satisfied with minimal effort; (2) those that can be satisfied but only at the cost of serious effort; (3) those that cannot be adequately satisfied no matter how much effort one makes. The power process is the process of satisfying the drives of the second group. The more drives there are in the third group, the more there is frustration, anger, eventually defeatism, depression, etc.
60. In modern industrial society natural human drives tend to be pushed into the first and third groups, and the second group tends to consist increasingly of artificially created drives.
61. In primitive societies, physical necessities generally fall into group 2: They can be obtained, but only at the cost of serious effort. But modern society tends to guaranty the physical necessities to everyone [9] in exchange for only minimal effort, hence physical needs are pushed into group 1. (There may be disagreement about whether the effort needed to hold a job is "minimal"; but usually, in lower- to middle-level jobs, whatever effort is required is merely that of OBEDIENCE. You sit or stand where you are told to sit or stand and do what you are told to do in the way you are told to do it. Seldom do you have to exert yourself seriously, and in any case you have hardly any autonomy in work, so that the need for the power process is not well served.)
62. Social needs, such as sex, love and status, often remain in group 2 in modern society, depending on the situation of the individual. [10] But, except for people who have a particularly strong drive for status, the effort required to fulfill the social drives is insufficient to satisfy adequately the need for the power process.
63. So certain artificial needs have been created that fall into group 2, hence serve the need for the power process. Advertising and marketing techniques have been developed that make many people feel they need things that their grandparents never desired or even dreamed of. It requires serious effort to earn enough money to satisfy these artificial needs, hence they fall into group 2. (But see paragraphs 80-82.) Modern man must satisfy his need for the power process largely through pursuit of the artificial needs created by the advertising and marketing industry [11], and through surrogate activities.
64. It seems that for many people, maybe the majority, these artificial forms of the power process are insufficient. A theme that appears repeatedly in the writings of the social critics of the second half of the 20th century is the sense of purposelessness that afflicts many people in modern society. (This purposelessness is often called by other names such as "anomic" or "middle-class vacuity.") We suggest that the so-called "identity crisis" is actually a search for a sense of purpose, often for commitment to a suitable surrogate activity. It may be that existentialism is in large part a response to the purposelessness of modern life. [12] Very widespread in modern society is the search for "fulfillment." But we think that for the majority of people an activity whose main goal is fulfillment (that is, a surrogate activity) does not bring completely satisfactory fulfillment. In other words, it does not fully satisfy the need for the power process. (See paragraph 41.) That need can be fully satisfied only through activities that have some external goal, such as physical necessities, sex, love, status, revenge, etc.
65. Moreover, where goals are pursued through earning money, climbing the status ladder or functioning as part of the system in some other way, most people are not in a position to pursue their goals AUTONOMOUSLY. Most workers are someone else's employee and, as we pointed out in paragraph 61, must spend their days doing what they are told to do in the way they are told to do it. Even people who are in business for themselves have only limited autonomy. It is a chronic complaint of small-business persons and entrepreneurs that their hands are tied by excessive government regulation. Some of these regulations are doubtless unnecessary, but for the most part government regulations are essential and inevitable parts of our extremely complex society. A large portion of small business today operates on the franchise system. It was reported in the Wall Street Journal a few years ago that many of the franchise-granting companies require applicants for franchises to take a personality test that is designed to EXCLUDE those who have creativity and initiative, because such persons are not sufficiently docile to go along obediently with the franchise system. This excludes from small business many of the people who most need autonomy.
66. Today people live more by virtue of what the system does FOR them or TO them than by virtue of what they do for themselves. And what they do for themselves is done more and more along channels laid down by the system. Opportunities tend to be those that the system provides, the opportunities must be exploited in accord with rules and regulations [13], and techniques prescribed by experts must be followed if there is to be a chance of success.
67. Thus the power process is disrupted in our society through a deficiency of real goals and a deficiency of autonomy in the pursuit of goals. But it is also disrupted because of those human drives that fall into group 3: the drives that one cannot adequately satisfy no matter how much effort one makes. One of these drives is the need for security. Our lives depend on decisions made by other people; we have no control over these decisions and usually we do not even know the people who make them. ("We live in a world in which relatively few peoplesmaybe 500 or 1,000smake the important decisions"sPhilip B. Heymann of Harvard Law School, quoted by Anthony Lewis, New York Times, April 21, 1995.) Our lives depend on whether safety standards at a nuclear power plant are properly maintained; on how much pesticide is allowed to get into our food or how much pollution into our air; on how skillful (or incompetent) our doctor is; whether we lose or get a job may depend on decisions made by government economists or corporation executives; and so forth. Most individuals are not in a position to secure themselves against these threats to more [than] a very limited extent. The individual's search for security is therefore frustrated, which leads to a sense of powerlessness.
68. It may be objected that primitive man is physically less secure than modern man, as is shown by his shorter life expectancy; hence modern man suffers from less, not more than the amount of insecurity that is normal for human beings. But psychological security does not closely correspond with physical security. What makes us FEEL secure is not so much objective security as a sense of confidence in our ability to take care of ourselves. Primitive man, threatened by a fierce animal or by hunger, can fight in self-defense or travel in search of food. He has no certainty of success in these efforts, but he is by no means helpless against the things that threaten him. The modern individual on the other hand is threatened by many things against which he is helpless: nuclear accidents, carcinogens in food, environmental pollution, war, increasing taxes, invasion of his privacy by large organizations, nationwide social or economic phenomena that may disrupt his way of life.
69. It is true that primitive man is powerless against some of the things that threaten him; disease for example. But he can accept the risk of disease stoically. It is part of the nature of things, it is no one's fault, unless it is the fault of some imaginary, impersonal demon. But threats to the modern individual tend to be MAN-MADE. They are not the results of chance but are IMPOSED on him by other persons whose decisions he, as an individual, is unable to influence. Consequently he feels frustrated, humiliated and angry.
70. Thus primitive man for the most part has his security in his own hands (either as an individual or as a member of a SMALL group) whereas the security of modern man is in the hands of persons or organizations that are too remote or too large for him to be able personally to influence them. So modern man's drive for security tends to fall into groups 1 and 3; in some areas (food, shelter etc.) his security is assured at the cost of only trivial effort, whereas in other areas he CANNOT attain security. (The foregoing greatly simplifies the real situation, but it does indicate in a rough, general way how the condition of modern man differs from that of primitive man.)
71. People have many transitory drives or impulses that are necessarily frustrated in modern life, hence fall into group 3. One may become angry, but modern society cannot permit fighting. In many situations it does not even permit verbal aggression. When going somewhere one may be in a hurry, or one may be in a mood to travel slowly, but one generally has no choice but to move with the flow of traffic and obey the traffic signals. One may want to do one's work in a different way, but usually one can work only according to the rules laid down by one's employer. In many other ways as well, modern man is strapped down by a network of rules and regulations (explicit or implicit) that frustrate many of his impulses and thus interfere with the power process. Most of these regulations cannot be dispensed with, because they are necessary for the functioning of industrial society.
72. Modern society is in certain respects extremely permissive. In matters that are irrelevant to the functioning of the system we can generally do what we please. We can believe in any religion we like (as long as it does not encourage behavior that is dangerous to the system). We can go to bed with anyone we like (as long as we practice "safe sex"). We can do anything we like as long as it is UNIMPORTANT. But in all IMPORTANT matters the system tends increasingly to regulate our behavior.
73. Behavior is regulated not only through explicit rules and not only by the government. Control is often exercised through indirect coercion or through psychological pressure or manipulation, and by organizations other than the government, or by the system as a whole. Most large organizations use some form of propaganda [14] to manipulate public attitudes or behavior. Propaganda is not limited to "commercials" and advertisements, and sometimes it is not even consciously intended as propaganda by the people who make it. For instance, the content of entertainment programming is a powerful form of propaganda. An example of indirect coercion: There is no law that says we have to go to work every day and follow our employer's orders. Legally there is nothing to prevent us from going to live in the wild like primitive people or from going into business for ourselves. But in practice there is very little wild country left, and there is room in the economy for only a limited number of small business owners. Hence most of us can survive only as someone else's employee.
74. We suggest that modern man's obsession with longevity, and with maintaining physical vigor and sexual attractiveness to an advanced age, is a symptom of unfulfillment resulting from deprivation with respect to the power process. The "mid-life crisis" also is such a symptom. So is the lack of interest in having children that is fairly common in modern society but almost unheard-of in primitive societies.
75. In primitive societies life is a succession of stages. The needs and purposes of one stage having been fulfilled, there is no particular reluctance about passing on to the next stage. A young man goes through the power process by becoming a hunter, hunting not for sport or for fulfillment but to get meat that is necessary for food. (In young women the process is more complex, with greater emphasis on social power; we won't discuss that here.) This phase having been successfully passed through, the young man has no reluctance about settling down to the responsibilities of raising a family. (In contrast, some modern people indefinitely postpone having children because they are too busy seeking some kind of "fulfillment." We suggest that the fulfillment they need is adequate experience of the power processswith real goals instead of the artificial goals of surrogate activities.) Again, having successfully raised his children, going through the power process by providing them with the physical necessities, the primitive man feels that his work is done and he is prepared to accept old age (if he survives that long) and death. Many modern people, on the other hand, are disturbed by the prospect of physical deterioration and death, as is shown by the amount of effort they expend trying to maintain their physical condition, appearance and health. We argue that this is due to unfulfillment resulting from the fact that they have never put their physical powers to any practical use, have never gone through the power process using their bodies in a serious way. It is not the primitive man, who has used his body daily for practical purposes, who fears the deterioration of age, but the modern man, who has never had a practical use for his body beyond walking from his car to his house. It is the man whose need for the power process has been satisfied during his life who is best prepared to accept the end of that life.
76. In response to the arguments of this section someone will say, "Society must find a way to give people the opportunity to go through the power process." For such people the value of the opportunity is destroyed by the very fact that society gives it to them. What they need is to find or make their own opportunities. As long as the system GIVES them their opportunities it still has them on a leash. To attain autonomy they must get off that leash.
HOW SOME People adjust
77. Not everyone in industrial-technological society suffers from psychological problems. Some people even profess to be quite satisfied with society as it is. We now discuss some of the reasons why people differ so greatly in their response to modern society.
78. First, there doubtless are differences in the strength of the drive for power. Individuals with a weak drive for power may have relatively little need to go through the power process, or at least relatively little need for autonomy in the power process. These are docile types who would have been happy as plantation darkies in the Old South. (We don't mean to sneer at the "plantation darkies" of the Old South. To their credit, most of the slaves were NOT content with their servitude. We do sneer at people who ARE content with servitude.)
79. Some people may have some exceptional drive, in pursuing which they satisfy their need for the power process. For example, those who have an unusually strong drive for social status may spend their whole lives climbing the status ladder without ever getting bored with that game.
80. People vary in their susceptibility to advertising and marketing techniques. Some are so susceptible that, even if they make a great deal of money, they cannot satisfy their constant craving for the the shiny new toys that the marketing industry dangles before their eyes. So they always feel hard-pressed financially even if their income is large, and their cravings are frustrated.
81. Some people have low susceptibility to advertising and marketing techniques. These are the people who aren't interested in money. Material acquisition does not serve their need for the power process.
82. People who have medium susceptibility to advertising and marketing techniques are able to earn enough money to satisfy their craving for goods and services, but only at the cost of serious effort (putting in overtime, taking a second job, earning promotions, etc.). Thus material acquisition serves their need for the power process. But it does not necessarily follow that their need is fully satisfied. They may have insufficient autonomy in the power process (their work may consist of following orders) and some of their drives may be frustrated (e.g., security, aggression). (We are guilty of oversimplification in paragraphs 80-82 because we have assumed that the desire for material acquisition is entirely a creation of the advertising and marketing industry. Of course it's not that simple. [11]
83. Some people partly satisfy their need for power by identifying themselves with a powerful organization or mass movement. An individual lacking goals or power joins a movement or an organization, adopts its goals as his own, then works toward those goals. When some of the goals are attained, the individual, even though his personal efforts have played only an insignificant part in the attainment of the goals, feels (through his identif ication with the movement or organization) as if he had gone through the power process. This phenomenon was exploited by the fascists, nazis and communists. Our society uses it too, though less crudely. Example: Manuel Noriega was an irritant to the U.S. (goal: punish Noriega). The U.S. invaded Panama (effort) and punished Noriega (attainment of goal). Thus the U.S. went through the power process and many Americans, because of their identification with the U.S., experienced the power process vicariously. Hence the widespread public approval of the Panama invasion; it gave people a sense of power. [15] We see the same phenomenon in armies, corporations, political parties, humanitarian organizations, religious or ideological movements. In particular, leftist movements tend to attract people who are seeking to satisfy their need for power. But for most people identification with a large organization or a mass movement does not fully satisfy the need for power.
84. Another way in which people satisfy their need for the power process is through surrogate activities. As we explained in paragraphs 38-40, a surrogate activity is an activity that is directed toward an artificial goal that the individual pursues for the sake of the "fulfillment" that he gets from pursuing the goal, not because he needs to attain the goal itself. For instance, there is no practical motive for building enormous muscles, hitting a little ball into a hole or acquiring a complete series of postage stamps. Yet many people in our society devote themselves with passion to bodybuilding, golf or stamp-collecting. Some people are more "other-directed" than others, and therefore will more readily attach importance to a surrogate activity simply because the people around them treat it as important or because society tells them it is important. That is why some people get very serious about essentially trivial activities such as sports, or bridge, or chess, or arcane scholarly pursuits, whereas others who are more clear-sighted never see these things as anything but the surrogate activities that they are, and consequently never attach enough importance to them to satisfy their need for the power process in that way. It only remains to point out that in many cases a person's way of earning a living is also a surrogate activity. Not a PURE surrogate activity, since part of the motive for the activity is to gain the physical necessities and (for some people) social status and the luxuries that advertising makes them want. But many people put into their work far more effort than is necessary to earn whatever money and status they require, and this extra effort constitutes a surrogate activity. This extra effort, together with the emotional investment that accompanies it, is one of the most potent forces acting toward the continual development and perfecting of the system, with negative consequences for individual freedom (see paragraph 131). Especially, for the most creative scientists and engineers, work tends to be largely a surrogate activity. This point is so important that it deserves a separate discussion, which we shall give in a moment (paragraphs 87-92).
85. In this section we have explained how many people in modern society do satisfy their need for the power process to a greater or lesser extent. But we think that for the majority of people the need for the power process is not fully satisfied. In the first place, those who have an insatiable drive for status, or who get firmly "hooked" on a surrogate activity, or who identify strongly enough with a movement or organization to satisfy their need for power in that way, are exceptional personalities. Others are not fully satisfied with surrogate activities or by identification with an organization (see paragraphs 41, 64). In the second place, too much control is imposed by the system through explicit regulation or through socialization, which results in a deficiency of autonomy, and in frustration due to the impossibility of attaining certain goals and the necessity of restraining too many impulses.
86. But even if most people in industrial-technological society were well satisfied, we (FC) would still be opposed to that form of society, because (among other reasons) we consider it demeaning to fulfill one's need for the power process through surrogate activities or through identification with an organization, rather than through pursuit of real goals.
THE MOTIVES OF SCIENTISTS
87. Science and technology provide the most important examples of surrogate activities. Some scientists claim that they are motivated by "curiosity" or by a desire to "benefit humanity." But it is easy to see that neither of these can be the principal motive of most scientists. As for "curiosity," that notion is simply absurd. Most scientists work on highly specialized problems that are not the object of any normal curiosity. For example, is an astronomer, a mathematician or an entomologist curious about the properties of isopropyltrimethylmethane? Of course not. Only a chemist is curious about such a thing, and he is curious about it only because chemistry is his surrogate activity. Is the chemist curious about the appropriate classification of a new species of beetle? No. That question is of interest only to the entomologist, and he is interested in it only because entomology is his surrogate activity. If the chemist and the entomologist had to exert themselves seriously to obtain the physical necessities, and if that effort exercised their abilities in an interesting way but in some nonscientific pursuit, then they wouldn't give a damn about isopropyltrimethylmethane or the classification of beetles. Suppose that lack of funds for postgraduate education had led the chemist to become an insurance broker instead of a chemist. In that case he would have been very interested in insurance matters but would have cared nothing about isopropyltrimethylmethane. In any case it is not normal to put into the satisfaction of mere curiosity the amount of time and effort that scientists put into their work. The "curiosity" explanation for the scientists' motive just doesn't stand up.
88. The "benefit of humanity" explanation doesn't work any better. Some scientific work has no conceivable relation to the welfare of the human racesmost of archaeology or comparative linguistics for example. Some other areas of science present obviously dangerous possibilities. Yet scientists in these areas are just as enthusiastic about their work as those who develop vaccines or study air pollution. Consider the case of Dr. Edward Teller, who had an obvious emotional involvement in promoting nuclear power plants. Did this involvement stem from a desire to benefit humanity? If so, then why didn't Dr. Teller get emotional about other "humanitarian" causes? If he was such a humanitarian then why did he help to develop the H-bomb? As with many other scientific achievements, it is very much open to question whether nuclear power plants actually do benefit humanity. Does the cheap electricity outweigh the accumulating waste and the risk of accidents? Dr. Teller saw only one side of the question. Clearly his emotional involvement with nuclear power arose not from a desire to "benefit humanity" but from a personal fulfillment he got from his work and from seeing it put to practical use.
89. The same is true of scientists generally. With possible rare exceptions, their motive is neither curiosity nor a desire to benefit humanity but the need to go through the power process: to have a goal (a scientific problem to solve), to make an effort (research) and to attain the goal (solution of the problem.) Science is a surrogate activity because scientists work mainly for the fulfillment they get out of the work itself.
90. Of course, it's not that simple. Other motives do play a role for many scientists. Money and status for example. Some scientists may be persons of the type who have an insatiable drive for status (see paragraph 79) and this may provide much of the motivation for their work. No doubt the majority of scientists, like the majority of the general population, are more or less susceptible to advertising and marketing techniques and need money to satisfy their craving for goods and services. Thus science is not a PURE surrogate activity. But it is in large part a surrogate activity.
91. Also, science and technology constitute a power mass movement, and many scientists gratify their need for power through identification with this mass movement (see paragraph 83).
92. Thus science marches on blindly, without regard to the real welfare of the human race or to any other standard, obedient only to the psychological needs of the scientists and of the government officials and corporation executives who provide the funds for research.
THE NATURE OF FREEDOM
93. We are going to argue that industrial-technological society cannot be reformed in such a way as to prevent it from progressively narrowing the sphere of human freedom. But, because "freedom" is a word that can be interpreted in many ways, we must first make clear what kind of freedom we are concerned with.
94. By "freedom" we mean the opportunity to go through the power process, with real goals not the artificial goals of surrogate activities, and without interference, manipulation or supervision from anyone, especially from any large organization. Freedom means being in control (either as an individual or as a member of a SMALL group) of the life-and-death issues of one's existence; food, clothing, shelter and defense against whatever threats there may be in one's environment. Freedom means having power; not the power to control other people but the power to control the circumstances of one's own life. One does not have freedom if anyone else (especially a large organization) has power over one, no matter how benevolently, tolerantly and permissively that power may be exercised. It is important not to confuse freedom with mere permissiveness (see paragraph 72).
95. It is said that we live in a free society because we have a certain number of constitutionally guaranteed rights. But these are not as important as they seem. The degree of personal freedom that exists in a society is determined more by the economic and technological structure of the society than by its laws or its form of government. [16] Most of the Indian nations of New England were monarchies, and many of the cities of the Italian Renaissance were controlled by dictators. But in reading about these societies one gets the impression that they allowed far more personal freedom than our society does. In part this was because they lacked efficient mechanisms for enforcing the ruler's will: There were no modern, well-organized police forces, no rapid long-distance communications, no surveillance cameras, no dossiers of information about the lives of average citizens. Hence it was relatively easy to evade control.
96. As for our constitutional rights, consider for example that of freedom of the press. We certainly don't mean to knock that right; it is very important tool for limiting concentration of political power and for keeping those who do have political power in line by publicly exposing any misbehavior on their part. But freedom of the press is of very little use to the average citizen as an individual. The mass media are mostly under the control of large organizations that are integrated into the system. Anyone who has a little money can have something printed, or can distribute it on the Internet or in some such way, but what he has to say will be swamped by the vast volume of material put out by the media, hence it will have no practical effect. To make an impression on society with words is therefore almost impossible for most individuals and small groups. Take us (FC) for example. If we had never done anything violent and had submitted the present writings to a publisher, they probably would not have been accepted. If they had been been accepted and published, they probably would not have attracted many readers, because it's more fun to watch the entertainment put out by the media than to read a sober essay. Even if these writings had had many readers, most of these readers would soon have forgotten what they had read as their minds were flooded by the mass of material to which the media expose them. In order to get our message before the public with some chance of making a lasting impression, we've had to kill people.
97. Constitutional rights are useful up to a point, but they do not serve to guarantee much more than what might be called the bourgeois conception of freedom. According to the bourgeois conception, a "free" man is essentially an element of a social machine and has only a certain set of prescribed and delimited freedoms; freedoms that are designed to serve the needs of the social machine more than those of the individual. Thus the bourgeois's "free" man has economic freedom because that promotes growth and progress; he has freedom of the press because public criticism restrains misbehavior by political leaders; he has a right to a fair trial because imprisonment at the whim of the powerful would be bad for the system. This was clearly the attitude of Simon Bolivar. To him, people deserved liberty only if they used it to promote progress (progress as conceived by the bourgeois). Other bourgeois thinkers have taken a similar view of freedom as a mere means to collective ends. Chester C. Tan, "Chinese Political Thought in the Twentieth Century," page 202, explains the philosophy of the Kuomintang leader Hu Han-min: "An individual is granted rights because he is a member of society and his community life requires such rights. By community Hu meant the whole society of the nation." And on page 259 Tan states that according to Carsum Chang (Chang Chun-mai, head of the State Socialist Party in China) freedom had to be used in the interest of the state and of the people as a whole. But what kind of freedom does one have if one can use it only as someone else prescribes? FC's conception of freedom is not that of Bolivar, Hu, Chang or other bourgeois theorists. The trouble with such theorists is that they have made the development and application of social theories their surrogate activity. Consequently the theories are designed to serve the needs of the theorists more than the needs of any people who may be unlucky enough to live in a society on which the theories are imposed.
98. One more point to be made in this section: It should not be assumed that a person has enough freedom just because he SAYS he has enough. Freedom is restricted in part by psychological controls of which people are unconscious, and moreover many people's ideas of what constitutes freedom are governed more by social convention than by their real needs. For example, it's likely that many leftists of the oversocialized type would say that most people, including themselves, are socialized too little rather than too much, yet the oversocialized leftist pays a heavy psychological price for his high level of socialization.
SOME PRINCIPLES OF HISTORY
99. Think of history as being the sum of two components: an erratic component that consists of unpredictable events that follow no discernible pattern, and a regular component that consists of long-term historical trends. Here we are concerned with the long-term trends.
100. FIRST PRINCIPLE. If a SMALL change is made that affects a long-term historical trend, then the effect of that change will almost always be transitorysthe trend will soon revert to its original state. (Example: A reform movement designed to clean up political corruption in a society rarely has more than a short-term effect; sooner or later the reformers relax and corruption creeps back in. The level of political corruption in a given society tends to remain constant, or to change only slowly with the evolution of the society. Normally, a political cleanup will be permanent only if accompanied by widespread social changes; a SMALL change in the society won't be enough.) If a small change in a long-term historical trend appears to be permanent, it is only because the change acts in the direction in which the trend is already moving, so that the trend is not altered by only pushed a step ahead.
101. The first principle is almost a tautology. If a trend were not stable with respect to small changes, it would wander at random rather than following a definite direction; in other words it would not be a long-term trend at all.
102. SECOND PRINCIPLE. If a change is made that is sufficiently large to alter permanently a long-term historical trend, then it will alter the society as a whole. In other words, a society is a system in which all parts are interrelated, and you can't permanently change any important part without changing all other parts as well.
103. THIRD PRINCIPLE. If a change is made that is large enough to alter permanently a long-term trend, then the consequences for the society as a whole cannot be predicted in advance. (Unless various other societies have passed through the same change and have all experienced the same consequences, in which case one can predict on empirical grounds that another society that passes through the same change will be like to experience similar consequences.)
104. FOURTH PRINCIPLE. A new kind of society cannot be designed on paper. That is, you cannot plan out a new form of society in advance, then set it up and expect it to function as it was designed to do.
105. The third and fourth principles result from the complexity of human societies. A change in human behavior will affect the economy of a society and its physical environment; the economy will affect the environment and vice versa, and the changes in the economy and the environment will affect human behavior in complex, unpredictable ways; and so forth. The network of causes and effects is far too complex to be untangled and understood.
106. FIFTH PRINCIPLE. People do not consciously and rationally choose the form of their society. Societies develop through processes of social evolution that are not under rational human control.
107. The fifth principle is a consequence of the other four.
108. To illustrate: By the first principle, generally speaking an attempt at social reform either acts in the direction in which the society is developing anyway (so that it merely accelerates a change that would have occurred in any case) or else it has only a transitory effect, so that the society soon slips back into its old groove. To make a lasting change in the direction of development of any important aspect of a society, reform is insufficient and revolution is required. (A revolution does not necessarily involve an armed uprising or the overthrow of a government.) By the second principle, a revolution never changes only one aspect of a society, it changes the whole society; and by the third principle changes occur that were never expected or desired by the revolutionaries. By the fourth principle, when revolutionaries or utopians set up a new kind of society, it never works out as planned.
109. The American Revolution does not provide a counterexample. The American "Revolution" was not a revolution in our sense of the word, but a war of independence followed by a rather far-reaching political reform. The Founding Fathers did not change the direction of development of American society, nor did they aspire to do so. They only freed the development of American society from the retarding effect of British rule. Their political reform did not change any basic trend, but only pushed American political culture along its natural direction of development. British society, of which American society was an offshoot, had been moving for a long time in the direction of representative democracy. And prior to the War of Independence the Americans were already practicing a significant degree of representative democracy in the colonial assemblies. The political system established by the Constitution was modeled on the British system and on the colonial assemblies. With major alteration, to be suresthere is no doubt that the Founding Fathers took a very important step. But it was a step along the road that English-speaking world was already traveling. The proof is that Britain and all of its colonies that were populated predominantly by people of British descent ended up with systems of representative democracy essentially similar to that of the United States. If the Founding Fathers had lost their nerve and declined to sign the Declaration of Independence, our way of life today would not have been significantly different. Maybe we would have had somewhat closer ties to Britain, and would have had a Parliament and Prime Minister instead of a Congress and President. No big deal. Thus the American Revolution provides not a counterexample to our principles but a good illustration of them.
110. Still, one has to use common sense in applying the principles. They are expressed in imprecise language that allows latitude for interpretation, and exceptions to them can be found. So we present these principles not as inviolable laws but as rules of thumb, or guides to thinking, that may provide a partial antidote to naive ideas about the future of society. The principles should be borne constantly in mind, and whenever one reaches a conclusion that conflicts with them one should carefully reexamine one's thinking and retain the conclusion only if one has good, solid reasons for doing so.
INDUSTRIAL-TECHNOLOGICAL SOCIETY CANNOT BE REFORMED
111. The foregoing principles help to show how hopelessly difficult it would be to reform the industrial system in such a way as to prevent it from progressively narrowing our sphere of freedom. There has been a consistent tendency, going back at least to the Industrial Revolution for technology to strengthen the system at a high cost in individual freedom and local autonomy. Hence any change designed to protect freedom from technology would be contrary to a fundamental trend in the development of our society. Consequently, such a change either would be a transitory onessoon swamped by the tide of historysor, if large enough to be permanent would alter the nature of our whole society. This by the first and second principles. Moreover, since society would be altered in a way that could not be predicted in advance (third principle) there would be great risk. Changes large enough to make a lasting difference in favor of freedom would not be initiated because it would be realized that they would gravely disrupt the system. So any attempts at reform would be too timid to be effective. Even if changes large enough to make a lasting difference were initiated, they would be retracted when their disruptive effects became apparent. Thus, permanent changes in favor of freedom could be brought about only by persons prepared to accept radical, dangerous and unpredictable alteration of the entire system. In other words by revolutionaries, not reformers.
112. People anxious to rescue freedom without sacrificing the supposed benefits of technology will suggest naive schemes for some new form of society that would reconcile freedom with technology. Apart from the fact that people who make such suggestions seldom propose any practical means by which the new form of society could be set up in the first place, it follows from the fourth principle that even if the new form of society could be once established, it either would collapse or would give results very different from those expected.
113. So even on very general grounds it seems highly improbable that any way of changing society could be found that would reconcile freedom with modern technology. In the next few sections we will give more specific reasons for concluding that freedom and technological progress are incompatible.
RESTRICTION OF FREEDOM IS UNAVOIDABLE IN INDUSTRIAL SOCIETY
114. As explained in paragraphs 65-67, 70-73, modern man is strapped down by a network of rules and regulations, and his fate depends on the actions of persons remote from him whose decisions he cannot influence. This is not accidental or a result of the arbitrariness of arrogant bureaucrats. It is necessary and inevitable in any technologically advanced society. The system HAS TO regulate human behavior closely in order to function. At work people have to do what they are told to do, otherwise production would be thrown into chaos. Bureaucracies HAVE TO be run according to rigid rules. To allow any substantial personal discretion to lower-level bureaucrats would disrupt the system and lead to charges of unfairness due to differences in the way individual bureaucrats exercised their discretion. It is true that some restrictions on our freedom could be eliminated, but GENERALLY SPEAKING the regulation of our lives by large organizations is necessary for the functioning of industrial-technological society. The result is a sense of powerlessness on the part of the average person. It may be, however, that formal regulations will tend increasingly to be replaced by psychological tools that make us want to do what the system requires of us. (Propaganda [14], educational techniques, "mental health" programs, etc.)
115. The system HAS TO force people to behave in ways that are increasingly remote from the natural pattern of human behavior. For example, the system needs scientists, mathematicians and engineers. It can't function without them. So heavy pressure is put on children to excel in these fields. It isn't natural for an adolescent human being to spend the bulk of his time sitting at a desk absorbed in study. A normal adolescent wants to spend his time in active contact with the real world. Among primitive peoples the things that children are trained to do tend to be in reasonable harmony with natural human impulses. Among the American Indians, for example, boys were trained in active outdoor pursuits just the sort of thing that boys like. But in our society children are pushed into studying technical subjects, which most do grudgingly.
116. Because of the constant pressure that the system exerts to modify human behavior, there is a gradual increase in the number of people who cannot or will nottadjust to society's requirements: welfare leeches, youth-gang members, cultists, anti-government rebels, radical environmentalist saboteurs, dropouts and resisters of various kinds.
117. In any technologically advanced society the individual's fate MUST depend on decisions that he personally cannot influence to any great extent. A technological society cannot be broken down into small, autonomous communities, because production depends on the cooperation of very large numbers of people and machines. Such a society MUST be highly organized and decisions HAVE TO be made that affect very large numbers of people. When a decision affects, say, a million people, then each of the affected individuals has, on the average, only a one-millionth share in making the decision. What usually happens in practice is that decisions are made by public officials or corporation executives, or by technical specialists, but even when the public votes on a decision the number of voters ordinarily is too large for the vote of any one individual to be significant. [17] Thus most individuals are unable to influence measurably the major decisions that affect their lives. There is no conceivable way to remedy this in a technologically advanced society. The system tries to "solve" this problem by using propaganda to make people WANT the decisions that have been made for them, but even if this "solution" were completely successful in making people feel better, it would be demeaning.
118. Conservatives and some others advocate more "local autonomy." Local communities once did have autonomy, but such autonomy becomes less and less possible as local communities become more enmeshed with and dependent on large-scale systems like public utilities, computer networks, highway systems, the mass communications media, the modern health care system. Also operating against autonomy is the fact that technology applied in one location often affects people at other locations far way. Thus pesticide or chemical use near a creek may contaminate the water supply hundreds of miles downstream, and the greenhouse effect affects the whole world.
119. The system does not and cannot exist to satisfy human needs. Instead, it is human behavior that has to be modified to fit the needs of the system. This has nothing to do with the political or social ideology that may pretend to guide the technological system. It is the fault of technology, because the system is guided not by ideology but by technical necessity. [18] Of course the system does satisfy many human needs, but generally speaking it does this only to the extend that it is to the advantage of the system to do it. It is the needs of the system that are paramount, not those of the human being. For example, the system provides people with food because the system couldn't function if everyone starved; it attends to people's psychological needs whenever it can CONVENIENTLY do so, because it couldn't function if too many people became depressed or rebellious. But the system, for good, solid, practical reasons, must exert constant pressure on people to mold their behavior to the needs of the system. To much waste accumulating? The government, the media, the educational system, environmentalists, everyone inundates us with a mass of propaganda about recycling. Need more technical personnel? A chorus of voices exhorts kids to study science. No one stops to ask whether it is inhumane to force adolescents to spend the bulk of their time studying subjects most of them hate. When skilled workers are put out of a job by technical advances and have to undergo "retraining," no one asks whether it is humiliating for them to be pushed around in this way. It is simply taken for granted that everyone must bow to technical necessity. and for good reason: If human needs were put before technical necessity there would be economic problems, unemployment, shortages or worse. The concept of "mental health" in our society is defined largely by the extent to which an individual behaves in accord with the needs of the system and does so without showing signs of stress.
120. Efforts to make room for a sense of purpose and for autonomy within the system are no better than a joke. For example, one company, instead of having each of its employees assemble only one section of a catalogue, had each assemble a whole catalogue, and this was supposed to give them a sense of purpose and achievement. Some companies have tried to give their employees more autonomy in their work, but for practical reasons this usually can be done only to a very limited extent, and in any case employees are never given autonomy as to ultimate goalsstheir "autonomous" efforts can never be directed toward goals that they select personally, but only toward their employer's goals, such as the survival and growth of the company. Any company would soon go out of business if it permitted its employees to act otherwise. Similarly, in any enterprise within a socialist system, workers must direct their efforts toward the goals of the enterprise, otherwise the enterprise will not serve its purpose as part of the system. Once again, for purely technical reasons it is not possible for most individuals or small groups to have much autonomy in industrial society. Even the small-business owner commonly has only limited autonomy. Apart from the necessity of government regulation, he is restricted by the fact that he must fit into the economic system and conform to its requirements. For instance, when someone develops a new technology, the small-business person often has to use that technology whether he wants to or not, in order to remain competitive.
THE 'BAD' PARTS OF TECHNOLOGY CANNOT BE SEPARATED FROM THE 'GOOD' PARTS
121. A further reason why industrial society cannot be reformed in favor of freedom is that modern technology is a unified system in which all parts are dependent on one another. You can't get rid of the "bad" parts of technology and retain only the "good" parts. Take modern medicine, for example. Progress in medical science depends on progress in chemistry, physics, biology, computer science and other fields. Advanced medical treatments require expensive, high-tech equipment that can be made available only by a technologically progressive, economically rich society. Clearly you can't have much progress in medicine without the whole technological system and everything that goes with it.
122. Even if medical progress could be maintained without the rest of the technological system, it would by itself bring certain evils. Suppose for example that a cure for diabetes is discovered. People with a genetic tendency to diabetes will then be able to survive and reproduce as well as anyone else. Natural selection against genes for diabetes will cease and such genes will spread throughout the population. (This may be occurring to some extent already, since diabetes, while not curable, can be controlled through use of insulin.) The same thing will happen with many other diseases susceptibility to which is affected by genetic degradation of the population. The only solution will be some sort of eugenics program or extensive genetic engineering of human beings, so that man in the future will no longer be a creation of nature, or of chance, or of God (depending on your religious or philosophical opinions), but a manufactured product.
123. If you think that big government interferes in your life too much NOW, just wait till the government starts regulating the genetic constitution of your children. Such regulation will inevitably follow the introduction of genetic engineering of human beings, because the consequences of unregulated genetic engineering would be disastrous. [19]
124. The usual response to such concerns is to talk about "medical ethics." But a code of ethics would not serve to protect freedom in the face of medical progress; it would only make matters worse. A code of ethics applicable to genetic engineering would be in effect a means of regulating the genetic constitution of human beings. Somebody (probably the upper-middle class, mostly) would decide that such and such applications of genetic engineering were "ethical" and others were not, so that in effect they would be imposing their own values on the genetic constitution of the population at large. Even if a code of ethics were chosen on a completely democratic basis, the majority would be imposing their own values on any minorities who might have a different idea of what constituted an "ethical" use of genetic engineering. The only code of ethics that would truly protect freedom would be one that prohibited ANY genetic engineering of human beings, and you can be sure that no such code will ever be applied in a technological society. No code that reduced genetic engineering to a minor role could stand up for long, because the temptation presented by the immense power of biotechnology would be irresistible, especially since to the majority of people many of its applications will seem obviously and unequivocally good (eliminating physical and mental diseases, giving people the abilities they need to get along in today's world). Inevitably, genetic engineering will be used extensively, but only in ways consistent with the needs of the industrial-technological system. [20]
TECHNOLOGY IS A MORE POWERFUL SOCIAL FORCE THAN THE ASPIRATION FOR FREEDOM
125. It is not possible to make a LASTING compromise between technology and freedom, because technology is by far the more powerful social force and continually encroaches on freedom through REPEATED compromises. Imagine the case of two neighbors, each of whom at the outset owns the same amount of land, but one of whom is more powerful than the other. The powerful one demands a piece of the other's land. The weak one refuses. The powerful one says, "OK, let's compromise. Give me half of what I asked." The weak one has little choice but to give in. Some time later the powerful neighbor demands another piece of land, again there is a compromise, and so forth. By forcing a long series of compromises on the weaker man, the powerful one eventually gets all of his land. So it goes in the conflict between technology and freedom.
126. Let us explain why technology is a more powerful social force than the aspiration for freedom.
127. A technological advance that appears not to threaten freedom often turns out to threaten it very seriously later on. For example, consider motorized transport. A walking man formerly could go where he pleased, go at his own pace without observing any traffic regulations, and was independent of technological support-systems. When motor vehicles were introduced they appeared to increase man's freedom. They took no freedom away from the walking man, no one had to have an automobile if he didn't want one, and anyone who did choose to buy an automobile could travel much faster and farther than a walking man. But the introduction of motorized transport soon changed society in such a way as to restrict greatly man's freedom of locomotion. When automobiles became numerous, it became necessary to regulate their use extensively. In a car, especially in densely populated areas, one cannot just go where one likes at one's own pace one's movement is governed by the flow of traffic and by various traffic laws. One is tied down by various obligations: license requirements, driver test, renewing registration, insurance, maintenance required for safety, monthly payments on purchase price. Moreover, the use of motorized transport is no longer optional. Since the introduction of motorized transport the arrangement of our cities has changed in such a way that the majority of people no longer live within walking distance of their place of employment, shopping areas and recreational opportunities, so that they HAVE TO depend on the automobile for transportation. Or else they must use public transportation, in which case they have even less control over their own movement than when driving a car. Even the walker's freedom is now greatly restricted. In the city he continually has to stop to wait for traffic lights that are designed mainly to serve auto traffic. In the country, motor traffic makes it dangerous and unpleasant to walk along the highway. (Note this important point that we have just illustrated with the case of motorized transport: When a new item of technology is introduced as an option that an individual can accept or not as he chooses, it does not necessarily REMAIN optional. In many cases the new technology changes society in such a way that people eventually find themselves FORCED to use it.)
128. While technological progress AS A WHOLE continually narrows our sphere of freedom, each new technical advance CONSIDERED BY ITSELF appears to be desirable. Electricity, indoor plumbing, rapid long-distance communications ... how could one argue against any of these things, or against any other of the innumerable technical advances that have made modern society? It would have been absurd to resist the introduction of the telephone, for example. It offered many advantages and no disadvantages. Yet, as we explained in paragraphs 59-76, all these technical advances taken together have created a world in which the average man's fate is no longer in his own hands or in the hands of his neighbors and friends, but in those of politicians, corporation executives and remote, anonymous technicians and bureaucrats whom he as an individual has no power to influence. [21] The same process will continue in the future. Take genetic engineering, for example. Few people will resist the introduction of a genetic technique that eliminates a hereditary disease. It does no apparent harm and prevents much suffering. Yet a large number of genetic improvements taken together will make the human being into an engineered product rather than a free creation of chance (or of God, or whatever, depending on your religious beliefs).
129. Another reason why technology is such a powerful social force is that, within the context of a given society, technological progress marches in only one direction; it can never be reversed. Once a technical innovation has been introduced, people usually become dependent on it, so that they can never again do without it, unless it is replaced by some still more advanced innovation. Not only do people become dependent as individuals on a new item of technology, but, even more, the system as a whole becomes dependent on it. (Imagine what would happen to the system today if computers, for example, were eliminated.) Thus the system can move in only one direction, toward greater technologization. Technology repeatedly forces freedom to take a step back, but technology can never take a step backsshort of the overthrow of the whole technological system.
130. Technology advances with great rapidity and threatens freedom at many different points at the same time (crowding, rules and regulations, increasing dependence of individuals on large organizations, propaganda and other psychological techniques, genetic engineering, invasion of privacy through surveillance devices and computers, etc.). To hold back any ONE of the threats to freedom would require a long and difficult social struggle. Those who want to protect freedom are overwhelmed by the sheer number of new attacks and the rapidity with which they develop, hence they become apathetic and no longer resist. To fight each of the threats separately would be futile. Success can be hoped for only by fighting the technological system as a whole; but that is revolution, not reform.
131. Technicians (we use this term in its broad sense to describe all those who perform a specialized task that requires training) tend to be so involved in their work (their surrogate activity) that when a conflict arises between their technical work and freedom, they almost always decide in favor of their technical work. This is obvious in the case of scientists, but it also appears elsewhere: Educators, humanitarian groups, conservation organizations do not hesitate to use propaganda or other psychological techniques to help them achieve their laudable ends. Corporations and government agencies, when they find it useful, do not hesitate to collect information about individuals without regard to their privacy. Law enforcement agencies are frequently inconvenienced by the constitutional rights of suspects and often of completely innocent persons, and they do whatever they can do legally (or sometimes illegally) to restrict or circumvent those rights. Most of these educators, government officials and law officers believe in freedom, privacy and constitutional rights, but when these conflict with their work, they usually feel that their work is more important.
132. It is well known that people generally work better and more persistently when striving for a reward than when attempting to avoid a punishment or negative outcome. Scientists and other technicians are motivated mainly by the rewards they get through their work. But those who oppose technological invasions of freedom are working to avoid a negative outcome, consequently there are few who work persistently and well at this discouraging task. If reformers ever achieved a signal victory that seemed to set up a solid barrier against further erosion of freedom through technical progress, most would tend to relax and turn their attention to more agreeable pursuits. But the scientists would remain busy in their laboratories, and technology as it progresses would find ways, in spite of any barriers, to exert more and more control over individuals and make them always more dependent on the system.
133. No social arrangements, whether laws, institutions, customs or ethical codes, can provide permanent protection against technology. History shows that all social arrangements are transitory; they all change or break down eventually. But technological advances are permanent within the context of a given civilization. Suppose for example that it were possible to arrive at some social arrangements that would prevent genetic engineering from being applied to human beings, or prevent it from being applied in such a way as to threaten freedom and dignity. Still, the technology would remain waiting. Sooner or later the social arrangement would break down. Probably sooner, given the pace of change in our society. Then genetic engineering would begin to invade our sphere of freedom, and this invasion would be irreversible (short of a breakdown of technological civilization itself). Any illusions about achieving anything permanent through social arrangements should be dispelled by what is currently happening with environmental legislation. A few years ago its seemed that there were secure legal barriers preventing at least SOME of the worst forms of environmental degradation. A change in the political wind, and those barriers begin to crumble.
134. For all of the foregoing reasons, technology is a more powerful social force than the aspiration for freedom. But this statement requires an important qualification. It appears that during the next several decades the industrial-technological system will be undergoing severe stresses due to economic and environmental problems, and especially due to problems of human behavior (alienation, rebellion, hostility, a variety of social and psychological difficulties). We hope that the stresses through which the system is likely to pass will cause it to break down, or at least will weaken it sufficiently so that a revolution against it becomes possible. If such a revolution occurs and is successful, then at that particular moment the aspiration for freedom will have proved more powerful than technology.
135. In paragraph 125 we used an analogy of a weak neighbor who is left destitute by a strong neighbor who takes all his land by forcing on him a series of compromises. But suppose now that the strong neighbor gets sick, so that he is unable to defend himself. The weak neighbor can force the strong one to give him his land back, or he can kill him. If he lets the strong man survive and only forces him to give the land back, he is a fool, because when the strong man gets well he will again take all the land for himself. The only sensible alternative for the weaker man is to kill the strong one while he has the chance. In the same way, while the industrial system is sick we must destroy it. If we compromise with it and let it recover from its sickness, it will eventually wipe out all of our freedom.
SIMPLER SOCIAL PROBLEMS HAVE PROVED INTRACTABLE
136. If anyone still imagines that it would be possible to reform the system in such a way as to protect freedom from technology, let him consider how clumsily and for the most part unsuccessfully our society has dealt with other social problems that are far more simple and straightforward. Among other things, the system has failed to stop environmental degradation, political corruption, drug trafficking or domestic abuse.
137. Take our environmental problems, for example. Here the conflict of values is straightforward: economic expedience now versus saving some of our natural resources for our grandchildren. [22] But on this subject we get only a lot of blather and obfuscation from the people who have power, and nothing like a clear, consistent line of action, and we keep on piling up environmental problems that our grandchildren will have to live with. Attempts to resolve the environmental issue consist of struggles and compromises between different factions, some of which are ascendant at one moment, others at another moment. The line of struggle changes with the shifting currents of public opinion. This is not a rational process, nor is it one that is likely to lead to a timely and successful solution to the problem. Major social problems, if they get "solved" at all, are rarely or never solved through any rational, comprehensive plan. They just work themselves out through a process in which various competing groups pursuing their own (usually short-term) self-interest [23] arrive (mainly by luck) at some more or less stable modus vivendi. In fact, the principles we formulated in paragraphs 100-106 make it seem doubtful that rational, long-term social planning can EVER be successful.
138. Thus it is clear that the human race has at best a very limited capacity for solving even relatively straightforward social problems. How then is it going to solve the far more difficult and subtle problem of reconciling freedom with technology? Technology presents clear-cut material advantages, whereas freedom is an abstraction that means different things to different people, and its loss is easily obscured by propaganda and fancy talk.
139. And note this important difference: It is conceivable that our environmental problems (for example) may some day be settled through a rational, comprehensive plan, but if this happens it will be only because it is in the long-term interest of the system to solve these problems. But it is NOT in the interest of the system to preserve freedom or small-group autonomy. On the contrary, it is in the interest of the system to bring human behavior under control to the greatest possible extent. [24] Thus, while practical considerations may eventually force the system to take a rational, prudent approach to environmental problems, equally practical considerations will force the system to regulate human behavior ever more closely (preferably by indirect means that will disguise the encroachment on freedom). This isn't just our opinion. Eminent social scientists (e.g. James Q. Wilson) have stressed the importance of "socializing" people more effectively.
REVOLUTION IS EASIER THAN REFORM
140. We hope we have convinced the reader that the system cannot be reformed in such a way as to reconcile freedom with technology. The only way out is to dispense with the industrial-technological system altogether. This implies revolution, not necessarily an armed uprising, but certainly a radical and fundamental change in the nature of society.
141. People tend to assume that because a revolution involves a much greater change than reform does, it is more difficult to bring about than reform is. Actually, under certain circumstances revolution is much easier than reform. The reason is that a revolutionary movement can inspire an intensity of commitment that a reform movement cannot inspire. A reform movement merely offers to solve a particular social problem. A revolutionary movement offers to solve all problems at one stroke and create a whole new world; it provides the kind of ideal for which people will take great risks and make great sacrifices. For this reasons it would be much easier to overthrow the whole technological system than to put effective, permanent restraints on the development or application of any one segment of technology, such as genetic engineering, for example. Not many people will devote themselves with single-minded passion to imposing and maintaining restraints on genetic engineering, but under suitable conditions large numbers of people may devote themselves passionately to a revolution against the industrial-technological system. As we noted in paragraph 132, reformers seeking to limit certain aspects of technology would be working to avoid a negative outcome. But revolutionaries work to gain a powerful rewardsfulfillment of their revolutionary visionsand therefore work harder and more persistently than reformers do.
142. Reform is always restrained by the fear of painful consequences if changes go too far. But once a revolutionary fever has taken hold of a society, people are willing to undergo unlimited hardships for the sake of their revolution. This was clearly shown in the French and Russian Revolutions. It may be that in such cases only a minority of the population is really committed to the revolution, but this minority is sufficiently large and active so that it becomes the dominant force in society. We will have more to say about revolution in paragraphs 180-205.
CONTROL OF HUMAN BEHAVIOR
143. Since the beginning of civilization, organized societies have had to put pressures on human beings of the sake of the functioning of the social organism. The kinds of pressures vary greatly from one society to another. Some of the pressures are physical (poor diet, excessive labor, environmental pollution), some are psychological (noise, crowding, forcing human behavior into the mold that society requires). In the past, human nature has been approximately constant, or at any rate has varied only within cer tain bounds. Consequently, societies have been able to push people only up to certain limits. When the limit of human endurance has been passed, things start going wrong: rebellion, or crime, or corruption, or evasion of work, or depression and other mental problems, or an elevated death rate, or a declining birth rate or something else, so that either the society breaks down, or its functioning becomes too inefficient and it is (quickly or gradually, through conquest, attrition or evolution) replaced by some more efficient form of society. [25]
144. Thus human nature has in the past put certain limits on the development of societies. People could be pushed only so far and no farther. But today this may be changing, because modern technology is developing ways of modifying human beings.
145. Imagine a society that subjects people to conditions that make them terribly unhappy, then gives them drugs to take away their unhappiness. Science fiction? It is already happening to some extent in our own society. It is well known that the rate of clinical depression has been greatly increasing in recent decades. We believe that this is due to disruption of the power process, as explained in paragraphs 59-76. But even if we are wrong, the increasing rate of depression is certainly the result of SOME conditions that exist in today's society. Instead of removing the conditions that make people depressed, modern society gives them antidepressant drugs. In effect, antidepressants are a means of modifying an individual's internal state in such a way as to enable him to tolerate social conditions that he would otherwise find intolerable. (Yes, we know that depression is often of purely genetic origin. We are referring here to those cases in which environment plays the predominant role.)
146. Drugs that affect the mind are only one example of the new methods of controlling human behavior that modern society is developing. Let us look at some of the other methods.
147. To start with, there are the techniques of surveillance. Hidden video cameras are now used in most stores and in many other places, computers are used to collect and process vast amounts of information about individuals. Information so obtained greatly increases the effectiveness of physical coercion (i.e., law enforcement). [26] Then there are the methods of propaganda, for which the mass communication media provide effective vehicles. Efficient techniques have been developed for winning elections, selling products, influencing public opinion. The entertainment industry serves as an important psychological tool of the system, possibly even when it is dishing out large amounts of sex and violence. Entertainment provides modern man with an essential means of escape. While absorbed in television, videos, etc., he can forget stress, anxiety, frustration, dissatisfaction. Many primitive peoples, when they don't have work to do, are quite content to sit for hours at a time doing nothing at all, because they are at peace with themselves and their world. But most modern people must be constantly occupied or entertained, otherwise they get "bored," i.e., they get fidgety, uneasy, irritable.
148. Other techniques strike deeper than the foregoing. Education is no longer a simple affair of paddling a kid's behind when he doesn't know his lessons and patting him on the head when he does know them. It is becoming a scientific technique for controlling the child's development. Sylvan Learning Centers, for example, have had great success in motivating children to study, and psychological techniques are also used with more or less success in many conventional schools. "Parenting" techniques that are taught to parents are designed to make children accept fundamental values of the system and behave in ways that the system finds desirable. "Mental health" programs, "intervention" techniques, psychotherapy and so forth are ostensibly designed to benefit individuals, but in practice they usually serve as methodsfor inducing individuals to think and behave as the system requires. (There is no contradiction here; an individual whose attitudes or behavior bring him into conflict with the system is up against a force that is too powerful for him to conquer or escape from, hence he is likely to suffer from stress, frustration, defeat. His path will be much easier if he thinks and behaves as the system requires. In that sense the system is acting for the benefit of the individual when it brainwashes him into conformity.) Child abuse in its gross and obvious forms is disapproved in most if not all cultures. Tormenting a child for a trivial reason or no reason at all is something that appalls almost everyone. But many psychologists interpret the concept of abuse much more broadly. Is spanking, when used as part of a rational and consistent system of discipline, a form of abuse? The question will ultimately be decided by whether or not spanking tends to produce behavior that makes a person fit in well with the existing system of society. In practice, the word "abuse" tends to be interpreted to include any method of child-rearing that produces behavior inconvenient for the system. Thus, when they go beyond the prevention of obvious, senseless cruelty, programs for preventing "child abuse" are directed toward the control of human behavior on behalf of the system.
149. Presumably, research will continue to increase the effectiveness of psychological techniques for controlling human behavior. But we think it is unlikely that psychological techniques alone will be sufficient to adjust human beings to the kind of society that technology is creating. Biological methods probably will have to be used. We have already mentioned the use of drugs in this connection. Neurology may provide other avenues for modifying the human mind. Genetic engineering of human beings is already beginning to occur in the form of "gene therapy," and there is no reason to assume that such methods will not eventually be used to modify those aspects of the body that affect mental functioning.
150. As we mentioned in paragraph 134, industrial society seems likely to be entering a period of severe stress, due in part to problems of human behavior and in part to economic and environmental problems. And a considerable proportion of the system's economic and environmental problems result from the way human beings behave. Alienation, low self-esteem, depression, hostility, rebellion; children who won't study, youth gangs, illegal drug use, rape, child abuse, other crimes, unsafe sex, teen pregnancy, population growth, political corruption, race hatred, ethnic rivalry, bitter ideological conflict (e.g., pro-choice vs. pro-life), political extremism, terrorism, sabotage, anti-government groups, hate groups. All these threaten the very survival of the system. The system will therefore be FORCED to use every practical means of controlling human behavior.
151. The social disruption that we see today is certainly not the result of mere chance. It can only be a result of the conditions of life that the system imposes on people. (We have argued that the most important of these conditions is disruption of the power process.) If the systems succeeds in imposing sufficient control over human behavior to assure its own survival, a new watershed in human history will have been passed. Whereas formerly the limits of human endurance have imposed limits on the development of societies (as we explained in paragraphs 143, 144), industrial-technological society will be able to pass those limits by modifying human beings, whether by psychological methods or biological methods or both. In the future, social systems will not be adjusted to suit the needs of human beings. Instead, human being will be adjusted to suit the needs of the system. [27]
152. Generally speaking, technological control over human behavior will probably not be introduced with a totalitarian intention or even through a conscious desire to restrict human freedom. [28] Each new step in the assertion of control over the humanmind will be taken as a rational response to a problem that faces society, such as curing alcoholism, reducing the crime rate or inducing young people to study science and engineering. In many cases there will be a humanitarian justification. For example, when a psychiatrist prescribes an anti-depressant for a depressed patient, he is clearly doing that individual a favor. It would be inhumane to withhold the drug from someone who needs it. When parents send their children to Sylvan Learning Centers to have them manipulated into becoming enthusiastic about their studies, they do so from concern for their children's welfare. It may be that some of these parents wish that one didn't have to have specialized training to get a job and that their kid didn't have to be brainwashed into becoming a computer nerd. But what can they do? They can't change society, and their child may be unemployable if he doesn't have certain skills. So they send him to Sylvan.
153. Thus control over human behavior will be introduced not by a calculated decision of the authorities but through a process of social evolution (RAPID evolution, however). The process will be impossible to resist, because each advance, considered by itself, will appear to be beneficial, or at least the evil involved in making the advance will appear to be beneficial, or at least the evil involved in making the advance will seem to be less than that which would result from not making it (see paragraph 127). Propaganda for example is used for many good purposes, such as discouraging child abuse or race hatred. [14] Sex education is obviously useful, yet the effect of sex education (to the extent that it is successful) is to take the shaping of sexual attitudes away from the family and put it into the hands of the state as represented by the public school system.
154. Suppose a biological trait is discovered that increases the likelihood that a child will grow up to be a criminal, and suppose some sort of gene therapy can remove this trait. [29] Of course most parents whose children possess the trait will have them undergo the therapy. It would be inhumane to do otherwise, since the child would probably have a miserable life if he grew up to be a criminal. But many or most primitive societies have a low crime rate in comparison with that of our society, even though they have neither high-tech methods of child-rearing nor harsh systems of punishment. Since there is no reason to suppose that more modern men than primitive men have innate predatory tendencies, the high crime rate of our society must be due to the pressures that modern conditions put on people, to which many cannot or will not adjust. Thus a treatment designed to remove potential criminal tendencies is at least in part a way of re-engineering people so that they suit the requirements of the system.
155. Our society tends to regard as a "sickness" any mode of thought or behavior that is inconvenient for the system, and this is plausible because when an individual doesn't fit into the system it causes pain to the individual as well as problems for the system. Thus the manipulation of an individual to adjust him to the system is seen as a "cure" for a "sickness" and therefore as good.
156. In paragraph 127 we pointed out that if the use of a new item of technology is INITIALLY optional, it does not necessarily REMAIN optional, because the new technology tends to change society in such a way that it becomes difficult or impossible for an individual to function without using that technology. This applies also to the technology of human behavior. In a world in which most children are put through a program to make them enthusiastic about studying, a parent will almost be forced to put his kid through such a program, because if he does not, then the kid will grow up to be, comparatively speaking, an ignoramus and therefore unemployable. Or suppose a biological treatment is discovered that, without undesirable side-effects, will greatly reduce the psychological stress from which so many people suffer in our society.If large numbers of people choose to undergo the treatment, then the general level of stress in society will be reduced, so that it will be possible for the system to increase the stress-producing pressures. In fact, something like this seems to have happened already with one of our society's most important psychological tools for enabling people to reduce (or at least temporarily escape from) stress, namely, mass entertainment (see paragraph 147). Our use of mass entertainment is "optional": No law requires us to watch television, listen to the radio, read magazines. Yet mass entertainment is a means of escape and stress-reduction on which most of us have become dependent. Everyone complains about the trashiness of television, but almost everyone watches it. A few have kicked the TV habit, but it would be a rare person who could get along today without using ANY form of mass entertainment. (Yet until quite recently in human history most people got along very nicely with no other entertainment than that which each local community created for itself.) Without the entertainment industry the system probably would not have been able to get away with putting as much stress-producing pressure on us as it does.
157. Assuming that industrial society survives, it is likely that technology will eventually acquire something approaching complete control over human behavior. It has been established beyond any rational doubt that human thought and behavior have a largely biological basis. As experimenters have demonstrated, feelings such as hunger, pleasure, anger and fear can be turned on and off by electrical stimulation of appropriate parts of the brain. Memories can be destroyed by damaging parts of the brain or they can be brought to the surface by electrical stimulation. Hallucinations can be induced or moods changed by drugs. There may or may not be an immaterial human soul, but if there is one it clearly is less powerful that the biological mechanisms of human behavior. For if that were not the case then researchers would not be able so easily to manipulate human feelings and behavior with drugs and electrical currents.
158. It presumably would be impractical for all people to have electrodes inserted in their heads so that they could be controlled by the authorities. But the fact that human thoughts and feelings are so open to biological intervention shows that the problem of controlling human behavior is mainly a technical problem; a problem of neurons, hormones and complex molecules; the kind of problem that is accessible to scientific attack. Given the outstanding record of our society in solving technical problems, it is overwhelmingly probable that great advances will be made in the control of human behavior.
159. Will public resistance prevent the introduction of technological control of human behavior? It certainly would if an attempt were made to introduce such control all at once. But since technological control will be introduced through a long sequence of small advances, there will be no rational and effective public resistance. (See paragraphs 127, 132, 153.)
160. To those who think that all this sounds like science fiction, we point out that yesterday's science fiction is today's fact. The Industrial Revolution has radically altered man's environment and way of life, and it is only to be expected that as technology is increasingly applied to the human body and mind, man himself will be altered as radically as his environment and way of life have been.
HUMAN RACE AT A CROSSROADS
161. But we have gotten ahead of our story. It is one thing to develop in the laboratory a series of psychological or biological techniques for manipulating human behavior and quite another to integrate these techniques into a functioning social system. The latter problem is the more difficult of the two. For example, while the techniques of educational psychology doubtless work quite well in the "lab schools" where they are developed, it is not necessarily easy to apply them effectively throughout our educational system. We all know what many of our schools are like. The teachers are too busy taking knives and guns away from the kids to subject them to the latest techniques for making them into computer nerds. Thus, in spite of all its technical advances relating to human behavior, the system to date has not been impressively successful in controlling human beings. The people whose behavior is fairly well under the control of the system are those of the type that might be called "bourgeois." But there are growing numbers of people who in one way or another are rebels against the system: welfare leaches, youth gangs, cultists, satanists, nazis, radical environmentalists, militiamen, etc.
162. The system is currently engaged in a desperate struggle to overcome certain problems that threaten its survival, among which the problems of human behavior are the most important. If the system succeeds in acquiring sufficient control over human behavior quickly enough, it will probably survive. Otherwise it will break down. We think the issue will most likely be resolved within the next several decades, say 40 to 100 years.
163. Suppose the system survives the crisis of the next several decades. By that time it will have to have solved, or at least brought under control, the principal problems that confront it, in particular that of "socializing" human beings; that is, making people sufficiently docile so that heir behavior no longer threatens the system. That being accomplished, it does not appear that there would be any further obstacle to the development of technology, and it would presumably advance toward its logical conclusion, which is complete control over everything on Earth, including human beings and all other important organisms. The system may become a unitary, monolithic organization, or it may be more or less fragmented and consist of a number of organizations coexisting in a relationship that includes elements of both cooperation and competition, just as today the government, the corporations and other large organizations both cooperate and compete with one another. Human freedom mostly will have vanished, because individuals and small groups will be impotent vis-a-vis large organizations armed with supertechnology and an arsenal of advanced psychological and biological tools for manipulating human beings, besides instruments of surveillance and physical coercion. Only a small number of people will have any real power, and even these probably will have only very limited freedom, because their behavior too will be regulated; just as today our politicians and corporation executives can retain their positions of power only as long as their behavior remains within certain fairly narrow limits.
164. Don't imagine that the systems will stop developing further techniques for controlling human beings and nature once the crisis of the next few decades is over and increasing control is no longer necessary for the system's survival. On the contrary, once the hard times are over the system will increase its control over people and nature more rapidly, because it will no longer be hampered by difficulties of the kind that it is currently experiencing. Survival is not the principal motive for extending control. As we explained in paragraphs 87-90, technicians and scientists carry on their work largely as a surrogate activity; that is, they satisfy their need for power by solving technical problems. They will continue to do this with unabated enthusiasm, and among the most interesting and challenging problems for them to solve will be those of understanding the human body and mind and intervening in their development. For the "good of humanity," of course.
165. But suppose on the other hand that the stresses of the coming decades prove to be too much for the system. If the system breaks down there may be a period of chaos, a "time of troubles" such as those that history has recorded at various epochs in the past. It is impossible to predict what would emerge from such a time of troubles, but at any rate the human race would be given a new chance. The greatest danger is that industrial society may begin to reconstitute itself within the first few years after the breakdown. Certainly there will be many people (power-hungry types especially) who will be anxious to get the factories running again.
166. Therefore two tasks confront those who hate the servitude to which the industrial system is reducing the human race. First, we must work to heighten the social stresses within the system so as to increase the likelihood that it will break down or be weakened sufficiently so that a revolution against it becomes possible. Second, it is necessary to develop and propagate an ideology that opposes technology and the industrial society if and when the system becomes sufficiently weakened. And such an ideology will help to assure that, if and when industrial society breaks down, its remnants will be smashed beyond repair, so that the system cannot be reconstituted. The factories should be destroyed, technical books burned, etc.
HUMAN SUFFERING
167. The industrial system will not break down purely as a result of revolutionary action. It will not be vulnerable to revolutionary attack unless its own internal problems of development lead it into very serious difficulties. So if the system breaks down it will do so either spontaneously, or through a process that is in part spontaneous but helped along by revolutionaries. If the breakdown is sudden, many people will die, since the world's population has become so overblown that it cannot even feed itself any longer without advanced technology. Even if the breakdown is gradual enough so that reduction of the population can occur more through lowering of the birth rate than through elevation of the death rate, the process of de-industrialization probably will be very chaotic and involve much suffering. It is naive to think it likely that technology can be phased out in a smoothly managed, orderly way, especially since the technophiles will fight stubbornly at every step. Is it therefore cruel to work for the breakdown of the system? Maybe, but maybe not. In the first place, revolutionaries will not be able to break the system down unless it is already in enough trouble so that there would be a good chance of its eventually breaking down by itself anyway; and the bigger the system grows, the more disastrous the consequences of its breakdown will be; so it may be that revolutionaries, by hastening the onset of the breakdown, will be reducing the extent of the disaster.
168. In the second place, one has to balance struggle and death against the loss of freedom and dignity. To many of us, freedom and dignity are more important than a long life or avoidance of physical pain. Besides, we all have to die some time, and it may be better to die fighting for survival, or for a cause, than to live a long but empty and purposeless life.
169. In the third place, it is not at all certain that survival of the system will lead to less suffering than breakdown of the system would. The system has already caused, and is continuing to cause, immense suffering all over the world. Ancient cultures, that for hundreds of years gave people a satisfactory relationship with each other and with their environment, have been shattered by contact with industrial society, and the result has been a whole catalogue of economic, environmental, social and psychological problems. One of the effects of the intrusion of industrial society has been that over much of the world traditional controls on population have been thrown out of balance. Hence the population explosion, with all that that implies. Then there is the psychological suffering that is widespread throughout the supposedly fortunate countries of the West (see paragraphs 44, 45). No one knows what will happen as a result of ozone depletion, the greenhouse effect and other environmental problems that cannot yet be foreseen. And, as nuclear proliferation has shown, new technology cannot be kept out of the hands of dictators and irresponsible Third World nations. Would you like to speculate about what Iraq or North Korea will do with genetic engineering?
170. "Oh!" say the technophiles, "Science is going to fix all that! We will conquer famine, eliminate psychological suffering, make everybody healthy and happy!" Yeah, sure. That's what they said 200 years ago. The Industrial Revolution was supposed to eliminate poverty, make everybody happy, etc. The actual result has been quite different. The technophiles are hopelessly naive (or self-deceiving) in their understanding of social problems. They are unaware of (or choose to ignore) the fact that when large changes, even seemingly beneficial ones, are introduced into a society, they lead to a long sequence of other changes, most of which are impossible to predict (paragraph 103). The result is disruption of the society. So it is very probable that in their attempts to end poverty and disease, engineer docile, happy personalities and so forth, the technophiles will create social systems that are terribly troubled, even more so than the present once. For example, the scientists boast that they will end famine by creating new, genetically engineered food plants. But this will allow the human population to keep expanding indefinitely, and it is well known that crowding leads to increased stress and aggression. This is merely one example of the PREDICTABLE problems that will arise. We emphasize that, as past experience has shown, technical progress will lead to other new problems that CANNOT be predicted in advance (paragraph 103). In fact, ever since the Industrial Revolution, technology has been creating new problems for society far more rapidly than it has been solving old ones. Thus it will take a long and difficult period of trial and error for the technophiles to work the bugs out of their Brave New World (if they every do). In the meantime there will be great suffering. So it is not at all clear that the survival of industrial society would involve less suffering than the breakdown of that society would. Technology has gotten the human race into a fix from which there is not likely to be any easy escape.
THE FUTURE
171. But suppose now that industrial society does survive the next several decades and that the bugs do eventually get worked out of the system, so that it functions smoothly. What kind of system will it be? We will consider several possibilities.
172. First let us postulate that the computer scientists succeed in developing intelligent machines that can do all things better than human beings can do them. In that case presumably all work will be done by vast, highly organized systems of machines and no human effort will be necessary. Either of two cases might occur. The machines might be permitted to make all of their own decisions without human oversight, or else human control over the machines might be retained.
173. If the machines are permitted to make all their own decisions, we can't make any conjectures as to the results, because it is impossible to guess how such machines might behave. We only point out that the fate of the human race would be at the mercy of the machines. It might be argued that the human race would never be foolish enough to hand over all power to the machines. But we are suggesting neither that the human race would voluntarily turn power over to the machines nor that the machines would willfully seize power. What we do suggest is that the human race might easily permit itself to drift into a position of such dependence on the machines that it would have no practical choice but to accept all of the machines' decisions. As society and the problems that face it become more and more complex and as machines become more and more intelligent, people will let machines make more and more of their decisions for them, simply because machine-made decisions will bring better results than man-made ones. Eventually a stage may be reached at which the decisions necessary to keep the system running will be so complex that human beings will be incapable of making them intelligently. At that stage the machines will be in effective control. People won't be able to just turn the machines off, because they will be so dependent on them that turning them off would amount to suicide.
174. On the other hand it is possible that human control over the machines may be retained. In that case the average man may have control over certain private machines of his own, such as his car or his personal computer, but control over large systems of machines will be in the hands of a tiny elitesjust as it is today, but with two differences. Due to improved techniques the elite will have greater control over the masses; and because human work will no longer be necessary the masses will be superfluous, a useless burden on the system. If the elite is ruthless they may simply decide to exterminate the mass of humanity. If they are humane they may use propaganda or other psychological or biological techniques to reduce the birth rate until the mass of humanity becomes extinct, leaving the world to the elite. Or, if the elite consists of soft-hearted liberals, they may decide to play the role of good shepherds to the rest of the human race. They will see to it that everyone's physical needs are satisfied, that all children are raised under psychologically hygienic conditions, that everyone has a wholesome hobby to keep him busy, and that anyone who may become dissatisfied undergoes "treatment" to cure his "problem." Of course, life will be so purposeless that people will have to be biologically or psychologically engineered either to remove their need for the power process or to make them "sublimate" their drive for power into some harmless hobby. These engineered human beings may be happy in such a society, but they most certainly will not be free. They will have been reduced to the status of domestic animals.
175. But suppose now that the computer scientists do not succeed in developing artificial intelligence, so that human work remains necessary. Even so, machines will take care of more and more of the simpler tasks so that there will be an increasing surplus of human workers at the lower levels of ability. (We see this happening already. There are many people who find it difficult or impossible to get work, because for intellectual or psychological reasons they cannot acquire the level of training necessary to make themselves useful in the present system.) On those who are employed, ever-increasing demands will be placed: They will need more and more training, more and more ability, and will have to be ever more reliable, conforming and docile, because they will be more and more like cells of a giant organism. Their tasks will be increasingly specialized, so that their work will be, in a sense, out of touch with the real world, being concentrated on one tiny slice of reality. The system will have to use any means that it can, whether psychological or biological, to engineer people to be docile, to have the abilities that the system requires and to "sublimate" their drive for power into some specialized task. But the statement that the people of such a society will have to be docile may require qualification. The society may find competitiveness useful, provided that ways are found of directing competitiveness into channels that serve the needs of the system. We can imagine a future society in which there is endless competition for positions of prestige and power. But no more than a very few people will ever reach the top, where the only real power is (see end of paragraph 163). Very repellent is a society in which a person can satisfy his need for power only by pushing large numbers of other people out of the way and depriving them of THEIR opportunity for power.
176. One can envision scenarios that incorporate aspects of more than one of the possibilities that we have just discussed. For instance, it may be that machines will take over most of the work that is of real, practical importance, but that human beings will be kept busy by being given relatively unimportant work. It has been suggested, for example, that a great development of the service industries might provide work for human beings. Thus people would spent their time shining each other's shoes, driving each other around in taxicabs, making handicrafts for one another, waiting on each other's tables, etc. This seems to us a thoroughly contemptible way for the human race to end up, and we doubt that many people would find fulfilling lives in such pointless busy-work. They would seek other, dangerous outlets (drugs, crime, "cults," hate groups) unless they were biologically or psychologically engineered to adapt them to such a way of life.
177. Needless to say, the scenarios outlined above do not exhaust all the possibilities. They only indicate the kinds of outcomes that seem to us most likely. But we can envision no plausible scenarios that are any more palatable than the ones we've just described. It is overwhelmingly probable that if the industrial-technological system survives the next 40 to 100 years, it will by that time have developed certain general characteristics: Individuals (at least those of the "bourgeois" type, who are integrated into the system and make it run, and who therefore have all the power) will be more dependent than ever on large organizations; they will be more "socialized" than ever and their physical and mental qualities to a significant extent (possibly to a very great extent) will be those that are engineered into them rather than being the results of chance (or of God's will, or whatever); and whatever may be left of wild nature will be reduced to remnants preserved for scientific study and kept under the supervision and management of scientists (hence it will no longer be truly wild). In the long run (say a few centuries from now) it is likely that neither the human race nor any other important organisms will exist as we know them today, because once you start modifying organisms through genetic engineering there is no reason to stop at any particular point, so that the modifications will probably continue until man and other organisms have been utterly transformed.
178. Whatever else may be the case, it is certain that technology is creating for human beings a new physical and social environment radically different from the spectrum of environments to which natural selection has adapted the human race physically and psychologically. If man is not adjusted to this new environment by being artificially re-engineered, then he will be adapted to it through a long and painful process of natural selection. The former is far more likely than the latter.
179. It would be better to dump the whole stinking system and take the consequences.
STRATEGY
180. The technophiles are taking us all on an utterly reckless ride into the unknown. Many people understand something of what technological progress is doing to us yet take a passive attitude toward it because they think it is inevitable. But we (FC) don't think it is inevitable. We think it can be stopped, and we will give here some indications of how to go about stopping it.
181. As we stated in paragraph 166, the two main tasks for the present are to promote social stress and instability in industrial society and to develop and propagate an ideology that opposes technology and the industrial system. When the system becomes sufficiently stressed and unstable, a revolution against technology may be possible. The pattern would be similar to that of the French and Russian Revolutions. French society and Russian society, for several decades prior to their respective revolutions, showed increasing signs of stress and weakness. Meanwhile, ideologies were being developed that offered a new world view that was quite different from the old one. In the Russian case, revolutionaries were actively working to undermine the old order. Then, when the old system was put under sufficient additional stress (by financial crisis in France, by military defeat in Russia) it was swept away by revolution. What we propose is something along the same lines.
182. It will be objected that the French and Russian Revolutions were failures. But most revolutions have two goals. One is to destroy an old form of society and the other is to set up the new form of society envisioned by the revolutionaries. The French and Russian revolutionaries failed (fortunately!) to create the new kind of society of which they dreamed, but they were quite successful in destroying the old society. We have no illusions about the feasibility of creating a new, ideal form of society. Our goal is only to destroy the existing form of society.
183. But an ideology, in order to gain enthusiastic support, must have a positive ideal as well as a negative one; it must be FOR something as well as AGAINST something. The positive ideal that we propose is Nature. That is, WILD nature: those aspects of the functioning of the Earth and its living things that are independent of human management and free of human interference and control. And with wild nature we include human nature, by which we mean those aspects of the functioning of the human individual that are not subject to regulation by organized society but are products of chance, or free will, or God (depending on your religious or philosophical opinions).
184. Nature makes a perfect counter-ideal to technology for several reasons. Nature (that which is outside the power of the system) is the opposite of technology (which seeks to expand indefinitely the power of the system). Most people will agree that nature is beautiful; certainly it has tremendous popular appeal. The radical environmentalists ALREADY hold an ideology that exalts nature and opposes technology. [30] It is not necessary for the sake of nature to set up some chimerical utopia or any new kind of social order. Nature takes care of itself: It was a spontaneous creation that existed long before any human society, and for countless centuries many different kinds of human societies coexisted with nature without doing it an excessive amount of damage. Only with the Industrial Revolution did the effect of human society on nature become really devastating. To relieve the pressure on nature it is not necessary to create a special kind of social system, it is only necessary to get rid of industrial society. Granted, this will not solve all problems. Industrial society has already done tremendous damage to nature and it will take a very long time for the scars to heal. Besides, even pre-industrial societies can do significant damage to nature. Nevertheless, getting rid of industrial society will accomplish a great deal. It will relieve the worst of the pressure on nature so that the scars can begin to heal. It will remove the capacity of organized society to keep increasing its control over nature (including human nature). Whatever kind of society may exist after the demise of the industrial system, it is certain that most people will live close to nature, because in the absence of advanced technology there is no other way that people CAN live. To feed themselves they must be peasants or herdsmen or fishermen or hunters, etc. And, generally speaking, local autonomy should tend to increase, because lack of advanced technology and rapid communications will limit the capacity of governments or other large organizations to control local communities.
185. As for the negative consequences of eliminating industrial societyswell, you can't eat your cake and have it too. To gain one thing you have to sacrifice another.
186. Most people hate psychological conflict. For this reason they avoid doing any serious thinking about difficult social issues, and they like to have such issues presented to them in simple, black-and-white terms: THIS is all good and THAT is all bad. The revolutionary ideology should therefore be developed on two levels.
187. On the more sophisticated level the ideology should address itself to people who are intelligent, thoughtful and rational. The object should be to create a core of people who will be opposed to the industrial system on a rational, thought-out basis, with full appreciation of the problems and ambiguities involved, and of the price that has to be paid for getting rid of the system. It is particularly important to attract people of this type, as they are capable people and will be instrumental in influencing others. These people should be addressed on as rational a level as possible. Facts should never intentionally be distorted and intemperate language should be avoided. This does not mean that no appeal can be made to the emotions, but in making such appeal care should be taken to avoid misrepresenting the truth or doing anything else that would destroy the intellectual respectability of the ideology.
188. On a second level, the ideology should be propagated in a simplified form that will enable the unthinking majority to see the conflict of technology vs. nature in unambiguous terms. But even on this second level the ideology should not be expressed in language that is so cheap, intemperate or irrational that it alienates people of the thoughtful and rational type. Cheap, intemperate propaganda sometimes achieves impressive short-term gains, but it will be more advantageous in the long run to keep the loyalty of a small number of intelligently committed people than to arouse the passions of an unthinking, fickle mob who will change their attitude as soon as someone comes along with a better propaganda gimmick. However, propaganda of the rabble-rousing type may be necessary when the system is nearing the point of collapse and there is a final struggle between rival ideologies to determine which will become dominant when the old world-view goes under.
189. Prior to that final struggle, the revolutionaries should not expect to have a majority of people on their side. History is made by active, determined minorities, not by the majority, which seldom has a clear and consistent idea of what it really wants. Until the time comes for the final push toward revolution [31], the task of revolutionaries will be less to win the shallow support of the majority than to build a small core of deeply committed people. As for the majority, it will be enough to make them aware of the existence of the new ideology and remind them of it frequently; though of course it will be desirable to get majority support to the extent that this can be done without weakening the core of seriously committed people.
190. Any kind of social conflict helps to destabilize the system, but one should be careful about what kind of conflict one encourages. The line of conflict should be drawn between the mass of the people and the power-holding elite of industrial society (politicians, scientists, upper-level business executives, government officials, etc.). It should NOT be drawn between the revolutionaries and the mass of the people. For example, it would be bad strategy for the revolutionaries to condemn Americans for their habits of consumption. Instead, the average American should be portrayed as a victim of the advertising and marketing industry, which has suckered him into buying a lot of junk that he doesn't need and that is very poor compensation for his lost freedom. Either approach is consistent with the facts. It is merely a matter of attitude whether you blame the advertising industry for manipulating the public or blame the public for allowing itself to be manipulated. As a matter of strategy one should generally avoid blaming the public.
191. One should think twice before encouraging any other social conflict than that between the power-holding elite (which wields technology) and the general public (over which technology exerts its power). For one thing, other conflicts tend to distract attention from the important conflicts (between power-elite and ordinary people, between technology and nature); for another thing, other conflicts may actually tend to encourage technologization, because each side in such a conflict wants to use technological power to gain advantages over its adversary. This is clearly seen in rivalries between nations. It also appears in ethnic conflicts within nations. For example, in America many black leaders are anxious to gain power for African Americans by placing back individuals in the technological power-elite. They want there to be many black government officials, sc ientists, corporation executives and so forth. In this way they are helping to absorb the African American subculture into the technological system. Generally speaking, one should encourage only those social conflicts that can be fitted into the framework of the conflicts of power-elite vs. ordinary people, technology vs nature.
192. But the way to discourage ethnic conflict is NOT through militant advocacy of minority rights (see paragraphs 21, 29). Instead, the revolutionaries should emphasize that although minorities do suffer more or less disadvantage, this disadvantage is of peripheral significance. Our real enemy is the industrial-technological system, and in the struggle against the system, ethnic distinctions are of no importance.
193. The kind of revolution we have in mind will not necessarily involve an armed uprising against any government. It may or may not involve physical violence, but it will not be a POLITICAL revolution. Its focus will be on technology and economics, not politics. [32]
194. Probably the revolutionaries should even AVOID assuming political power, whether by legal or illegal means, until the industrial system is stressed to the danger point and has proved itself to be a failure in the eyes of most people. Suppose for example that some "green" party should win control of the United States Congress in an election. In order to avoid betraying or watering down their own ideology they would have to take vigorous measures to turn economic growth into economic shrinkage. To the average man the results would appear disastrous: There would be massive unemployment, shortages of commodities, etc. Even if the grosser ill effects could be avoided through superhumanly skillful management, still people would have to begin giving up the luxuries to which they have become addicted. Dissatisfaction would grow, the "green" party would be voted out of office and the revolutionaries would have suffered a severe setback. For this reason the revolutionaries should not try to acquire political power until the system has gotten itself into such a mess that any hardships will be seen as resulting from the failures of the industrial system itself and not from the policies of the revolutionaries. The revolution against technology will probably have to be a revolution by outsiders, a revolution from below and not from above.
195. The revolution must be international and worldwide. It cannot be carried out on a nation-by-nation basis. Whenever it is suggested that the United States, for example, should cut back on technological progress or economic growth, people get hysterical and start screaming that if we fall behind in technology the Japanese will get ahead of us. Holy robots! The world will fly off its orbit if the Japanese ever sell more cars than we do! (Nationalism is a great promoter of technology.) More reasonably, it is argued that if the relatively democratic nations of the world fall behind in technology while nasty, dictatorial nations like China, Vietnam and North Korea continue to progress, eventually the dictators may come to dominate the world. That is why the industrial system should be attacked in all nations simultaneously, to the extent that this may be possible. True, there is no assurance that the industrial system can be destroyed at approximately the same time all over the world, and it is even conceivable that the attempt to overthrow the system could lead instead to the domination of the system by dictators. That is a risk that has to be taken. And it is worth taking, since the difference between a "democratic" industrial system and one controlled by dictators is small compared with the difference between an industrial system and a non-industrial one. [33] It might even be argued that an industrial system controlled by dictators would be preferable, because dictator-controlled systems usually have proved inefficient, hence they are presumably more likely to break down. Look at Cuba.
196. Revolutionaries might consider favoring measures that tend to bind the world economy into a unified whole. Free trade agreements like NAFTA and GATT are probably harmful to the environment in the short run, but in the long run they may perhaps be advantageous because they foster economic interdependence between nations. It will be easier to destroy the industrial system on a worldwide basis if the world economy is so unified that its breakdown in any one major nation will lead to its breakdown in all industrialized nations.
197. Some people take the line that modern man has too much power, too much control over nature; they argue for a more passive attitude on the part of the human race. At best these people are expressing themselves unclearly, because they fail to distinguish between power for LARGE ORGANIZATIONS and power for INDIVIDUALS and SMALL GROUPS. It is a mistake to argue for powerlessness and passivity, because people NEED power. Modern man as a collective entitysthat is, the industrial systemshas immense power over nature, and we (FC) regard this as evil. But modern INDIVIDUALS and SMALL GROUPS OF INDIVIDUALS have far less power than primitive man ever did. Generally speaking, the vast power of "modern man" over nature is exercised not by individuals or small groups but by large organizations. To the extent that the average modern INDIVIDUAL can wield the power of technology, he is permitted to do so only within narrow limits and only under the supervision and control of the system. (You need a license for everything and with the license come rules and regulations.) The individual has only those technological powers with which the system chooses to provide him. His PERSONAL power over nature is slight.
198. Primitive INDIVIDUALS and SMALL GROUPS actually had considerable power over nature; or maybe it would be better to say power WITHIN nature. When primitive man needed food he knew how to find and prepare edible roots, how to track game and take it with homemade weapons. He knew how to protect himself from heat, cold, rain, dangerous animals, etc. But primitive man did relatively little damage to nature because the COLLECTIVE power of primitive society was negligible compared to the COLLECTIVE power of industrial society.
199. Instead of arguing for powerlessness and passivity, one should argue that the power of the INDUSTRIAL SYSTEM should be broken, and that this will greatly INCREASE the power and freedom of INDIVIDUALS and SMALL GROUPS.
200. Until the industrial system has been thoroughly wrecked, the destruction of that system must be the revolutionaries' ONLY goal. Other goals would distract attention and energy from the main goal. More importantly, if the revolutionaries permit themselves to have any other goal than the destruction of technology, they will be tempted to use technology as a tool for reaching that other goal. If they give in to that temptation, they will fall right back into the technological trap, because modern technology is a unified, tightly organized system, so that, in order to retain SOME technology, one finds oneself obliged to retain MOST technology, hence one ends up sacrificing only token amounts of technology.
201. Suppose for example that the revolutionaries took "social justice" as a goal. Human nature being what it is, social justice would not come about spontaneously; it would have to be enforced. In order to enforce it the revolutionaries would have to retain central organization and control. For that they would need rapid long-distance transportation and communication, and therefore all the technology needed to support the transportation and communication systems. To feed and clothe poor people they would have to use agricultural and manufacturing technology. And so forth. So that the attempt to insure social justice would force them to retain most parts of the technological system. Not that we have anything against social justice, but it must not be allowed to interfere with the effort to get rid of the technological system.
202. It would be hopeless for revolutionaries to try to attack the system without using SOME modern technology. If nothing else they must use the communications media to spread their message. But they should use modern technology for only ONE purpose: to attack the technological system.
203. Imagine an alcoholic sitting with a barrel of wine in front of him. Suppose he starts saying to himself, "Wine isn't bad for you if used in moderation. Why, they say small amounts of wine are even good for you! It won't do me any harm if I take just one little drink.... " Well you know what is going to happen. Never forget that the human race with technology is just like an alcoholic with a barrel of wine.
204. Revolutionaries should have as many children as they can. There is strong scientific evidence that social attitudes are to a significant extent inherited. No one suggests that a social attitude is a direct outcome of a person's genetic constitution, but it appears that personality traits are partly inherited and that certain personality traits tend, within the context of our society, to make a person more likely to hold this or that social attitude. Objections to these findings have been raised, but the objections are feeble and seem to be ideologically motivated. In any event, no one denies that children tend on the average to hold social attitudes similar to those of their parents. From our point of view it doesn't matter all that much whether the attitudes are passed on genetically or through childhood training. In either case they ARE passed on.
205. The trouble is that many of the people who are inclined to rebel against the industrial system are also concerned about the population problems, hence they are apt to have few or no children. In this way they may be handing the world over to the sort of people who support or at least accept the industrial system. To insure the strength of the next generation of revolutionaries the present generation should reproduce itself abundantly. In doing so they will be worsening the population problem only slightly. And the important problem is to get rid of the industrial system, because once the industrial system is gone the world's population necessarily will decrease (see paragraph 167); whereas, if the industrial system survives, it will continue developing new techniques of food production that may enable the world's population to keep increasing almost indefinitely.
206. With regard to revolutionary strategy, the only points on which we absolutely insist are that the single overriding goal must be the elimination of modern technology, and that no other goal can be allowed to compete with this one. For the rest, revolutionaries should take an empirical approach. If experience indicates that some of the recommendations made in the foregoing paragraphs are not going to give good results, then those recommendations should be discarded.
TWO KINDS OF TECHNOLOGY
207. An argument likely to be raised against our proposed revolution is that it is bound to fail, because (it is claimed) throughout history technology has always progressed, never regressed, hence technological regression is impossible. But this claim is false.
208. We distinguish between two kinds of technology, which we will call small-scale technology and organization-dependent technology. Small-scale technology is technology that can be used by small-scale communities without outside assistance. Organization-dependent technology is technology that depends on large-scale social organization. We are aware of no significant cases of regression in small-scale technology. But organization-dependent technology DOES regress when the social organization on which it depends breaks down. Example: When the Roman Empire fell apart the Romans' small-scale technology survived because any clever village craftsman could build, for instance, a water wheel, any skilled smith could make steel by Roman methods, and so forth. But the Romans' organization-dependent technology DID regress. Their aqueducts fell into disrepair and were never rebuilt. Their techniques of road construction were lost. The Roman system of urban sanitation was forgotten, so that not until r ather recent times did the sanitation of European cities equal that of Ancient Rome.
209. The reason why technology has seemed always to progress is that, until perhaps a century or two before the Industrial Revolution, most technology was small-scale technology. But most of the technology developed since the Industrial Revolution is organization-dependent technology. Take the refrigerator for example. Without factory-made parts or the facilities of a post-industrial machine shop it would be virtually impossible for a handful of local craftsmen to build a refrigerator. If by some miracle they did succeed in building one it would be useless to them without a reliable source of electric power. So they would have to dam a stream and build a generator. Generators require large amounts of copper wire. Imagine trying to make that wire without modern machinery. And where would they get a gas suitable for refrigeration? It would be much easier to build an icehouse or preserve food by drying or picking, as was done before the invention of the refrigerator.
210. So it is clear that if the industrial system were once thoroughly broken down, refrigeration technology would quickly be lost. The same is true of other organization-dependent technology. And once this technology had been lost for a generation or so it would take centuries to rebuild it, just as it took centuries to build it the first time around. Surviving technical books would be few and scattered. An industrial society, if built from scratch without outside help, can only be built in a series of stages: You need tools to make tools to make tools to make tools ... . A long process of economic development and progress in social organization is required. And, even in the absence of an ideology opposed to technology, there is no reason to believe that anyone would be interested in rebuilding industrial society. The enthusiasm for "progress" is a phenomenon peculiar to the modern form of society, and it seems not to have existed prior to the 17th century or thereabouts.
211. In the late Middle Ages there were four main civilizations that were about equally "advanced": Europe, the Islamic world, India, and the Far East (China, Japan, Korea). Three of those civilizations remained more or less stable, and only Europe became dynamic. No one knows why Europe became dynamic at that time; historians have their theories but these are only speculation. At any rate, it is clear that rapid development toward a technological form of society occurs only under special conditions. So there is no reason to assume that a long-lasting technological regression cannot be brought about.
212. Would society EVENTUALLY develop again toward an industrial-technological form? Maybe, but there is no use in worrying about it, since we can't predict or control events 500 or 1,000 years in the future. Those problems must be dealt with by the people who will live at that time.
THE DANGER OF LEFTISM
213. Because of their need for rebellion and for membership in a movement, leftists or persons of similar psychological type often are unattracted to a rebellious or activist movement whose goals and membership are not initially leftist. The resulting influx of leftish types can easily turn a non-leftist movement into a leftist one, so that leftist goals replace or distort the original goals of the movement.
214. To avoid this, a movement that exalts nature and opposes technology must take a resolutely anti-leftist stance and must avoid all collaboration with leftists. Leftism is in the long run inconsistent with wild nature, with human freedom and with the elimination of modern technology. Leftism is collectivist; it seeks to bind together the entire world (both nature and the human race) into a unified whole. But this implies management of nature and of human life by organized society, and it requires advanced technology. You can't have a united world without rapid transportation and communication, you can't make all people love one another without sophisticated psychological techniques, you can't have a "planned society" without the necessary technological base. Above all, leftism is driven by the need for power, and the leftist seeks power on a collective basis, through identification with a mass movement or an organization. Leftism is unlikely ever to give up technology, because technology is too valuable a source of collective power.
215. The anarchist [34] too seeks power, but he seeks it on an individual or small-group basis; he wants individuals and small groups to be able to control the circumstances of their own lives. He opposes technology because it makes small groups dependent on large organizations.
216. Some leftists may seem to oppose technology, but they will oppose it only so long as they are outsiders and the technological system is controlled by non-leftists. If leftism ever becomes dominant in society, so that the technological system becomes a tool in the hands of leftists, they will enthusiastically use it and promote its growth. In doing this they will be repeating a pattern that leftism has shown again and again in the past. When the Bolsheviks in Russia were outsiders, they vigorously opposed censorship and the secret police, they advocated self-determination for ethnic minorities, and so forth; but as soon as they came into power themselves, they imposed a tighter censorship and created a more ruthless secret police than any that had existed under the tsars, and they oppressed ethnic minorities at least as much as the tsars had done. In the United States, a couple of decades ago when leftists were a minority in our universities, leftist professors were vigorous proponents of academic freedom, but today, in those of our universities where leftists have become dominant, they have shown themselves ready to take away from everyone else's academic freedom. (This is "political correctness.") The same will happen with leftists and technology: They will use it to oppress everyone else if they ever get it under their own control.
217. In earlier revolutions, leftists of the most power-hungry type, repeatedly, have first cooperated with non-leftist revolutionaries, as well as with leftists of a more libertarian inclination, and later have double-crossed them to seize power for themselves. Robespierre did this in the French Revolution, the Bolsheviks did it in the Russian Revolution, the communists did it in Spain in 1938 and Castro and his followers did it in Cuba. Given the past history of leftism, it would be utterly foolish for non-leftist revolutionaries today to collaborate with leftists.
218. Various thinkers have pointed out that leftism is a kind of religion. Leftism is not a religion in the strict sense because leftist doctrine does not postulate the existence of any supernatural being. But, for the leftist, leftism plays a psychological role much like that which religion plays for some people. The leftist NEEDS to believe in leftism; it plays a vital role in his psychological economy. His beliefs are not easily modified by logic or facts. He has a deep conviction that leftism is morally Right with a capital R, and that he has not only a right but a duty to impose leftist morality on everyone. (However, many of the people we are referring to as "leftists" do not think of themselves as leftists and would not describe their system of beliefs as leftism. We use the term "leftism" because we don't know of any better words to designate the spectrum of related creeds that includes the feminist, gay rights, political correctness, etc., movements, and because these movements have a strong affinity with the old left. See paragraphs 227-230.)
219. Leftism is a totalitarian force. Wherever leftism is in a position of power it tends to invade every private corner and force every thought into a leftist mold. In part this is because of the quasi-religious character of leftism; everything contrary to leftist beliefs represents Sin. More importantly, leftism is a totalitarian force because of the leftists' drive for power. The leftist seeks to satisfy his need for power through identification with a social movement and he tries to go through the power process by helping to pursue and attain the goals of the movement (see paragraph 83). But no matter how far the movement has gone in attaining its goals the leftist is never satisfied, because his activism is a surrogate activity (see paragraph 41). That is, the leftist's real motive is not to attain the ostensible goals of leftism; in reality he is motivated by the sense of power he gets from struggling for and then reaching a social goal. [35] Consequently the leftist is never satisfied with the goals he has already attained; his need for the power process leads him always to pursue some new goal. The leftist wants equal opportunities for minorities. When that is attained he insists on statistical equality of achievement by minorities. And as long as anyone harbors in some corner of his mind a negative attitude toward some minority, the leftist has to re-educated him. And ethnic minorities are not enough; no one can be allowed to have a negative attitude toward homosexuals, disabled people, fat people, old people, ugly people, and on and on and on. It's not enough that the public should be informed about the hazards of smoking; a warning has to be stamped on every package of cigarettes. Then cigarette advertising has to be restricted if not banned. The activists will never be satisfied until tobacco is outlawed, and after that it will be alcohol, then junk food, etc. Activists have fought gross child abuse, which is reasonable. But now they want to stop all spanking. When they have done that they will want to ban something else they consider unwholesome, then another thing and then another. They will never be satisfied until they have complete control over all child rearing practices. And then they will move on to another cause.
220. Suppose you asked leftists to make a list of ALL the things that were wrong with society, and then suppose you instituted EVERY social change that they demanded. It is safe to say that within a couple of years the majority of leftists would find something new to complain about, some new social "evil" to correct because, once again, the leftist is motivated less by distress at society's ills than by the need to satisfy his drive for power by imposing his solutions on society.
221. Because of the restrictions placed on their thoughts and behavior by their high level of socialization, many leftists of the over-socialized type cannot pursue power in the ways that other people do. For them the drive for power has only one morally acceptable outlet, and that is in the struggle to impose their morality on everyone.
222. Leftists, especially those of the oversocialized type, are True Believers in the sense of Eric Hoffer's book, "The True Believer." But not all True Believers are of the same psychological type as leftists. Presumably a true-believing nazi, for instance, is very different psychologically from a true-believing leftist. Because of their capacity for single-minded devotion to a cause, True Believers are a useful, perhaps a necessary, ingredient of any revolutionary movement. This presents a problem with which we must admit we don't know how to deal. We aren't sure how to harness the energies of the True Believer to a revolution against technology. At present all we can say is that no True Believer will make a safe recruit to the revolution unless his commitment is exclusively to the destruction of technology. If he is committed also to another ideal, he may want to use technology as a tool for pursuing that other ideal (see paragraphs 220, 221).
223. Some readers may say, "This stuff about leftism is a lot of crap. I know John and Jane who are leftish types and they don't have all these totalitarian tendencies." It's quite true that many leftists, possibly even a numerical majority, are decent people who sincerely believe in tolerating others' values (up to a point) and wouldn't want to use high-handed methods to reach their social goals. Our remarks about leftism are not meant to apply to every individual leftist but to describe the general character of leftism as a movement. And the general character of a movement is not necessarily determined by the numerical proportions of the various kinds of people involved in the movement.
224. The people who rise to positions of power in leftist movements tend to be leftists of the most power-hungry type, because power-hungry people are those who strive hardest to get into positions of power. Once the power-hungry types have captured control of the movement, there are many leftists of a gentler breed who inwardly disapprove of many of the actions of the leaders, but cannot bring themselves to oppose them. They NEED their faith in the movement, and because they cannot give up this faith they go along with the leaders. True, SOME leftists do have the guts to oppose the totalitarian tendencies that emerge, but they generally lose, because the power-hungry types are better organized, are more ruthless and Machiavellian and have taken care to build themselves a strong power base.
225. These phenomena appeared clearly in Russia and other countries that were taken over by leftists. Similarly, before the breakdown of communism in the USSR, leftish types in the West would seldom criticize that country. If prodded they would admit that the USSR did many wrong things, but then they would try to find excuses for the communists and begin talking about the faults of the West. They always opposed Western military resistance to communist aggression. Leftish types all over the world vigorously protested the U.S. military action in Vietnam, but when the USSR invaded Afghanistan they did nothing. Not that they approved of the Soviet actions; but because of their leftist faith, they just couldn't bear to put themselves in opposition to communism. Today, in those of our universities where "political correctness" has become dominant, there are probably many leftish types who privately disapprove of the suppression of academic freedom, but they go along with it anyway.
226. Thus the fact that many individual leftists are personally mild and fairly tolerant people by no means prevents leftism as a whole form having a totalitarian tendency.
227. Our discussion of leftism has a serious weakness. It is still far from clear what we mean by the word "leftist." There doesn't seem to be much we can do about this. Today leftism is fragmented into a whole spectrum of activist movements. Yet not all activist movements are leftist, and some activist movements (e.g., radical environmentalism) seem to include both personalities of the leftist type and personalities of thoroughly un-leftist types who ought to know better than to collaborate with leftists. Varieties of leftists fade out gradually into varieties of non-leftists and we ourselves would often be hard-pressed to decide whether a given individual is or is not a leftist. To the extent that it is defined at all, our conception of leftism is defined by the discussion of it that we have given in this article, and we can only advise the reader to use his own judgment in deciding who is a leftist.
228. But it will be helpful to list some criteria for diagnosing leftism. These criteria cannot be applied in a cut and dried manner. Some individuals may meet some of the criteria without being leftists, some leftists may not meet any of the criteria. Again, you just have to use your judgment.
229. The leftist is oriented toward large-scale collectivism. He emphasizes the duty of the individual to serve society and the duty of society to take care of the individual. He has a negative attitude toward individualism. He often takes a moralistic tone. He tends to be for gun control, for sex education and other psychologically "enlightened" educational methods, for social planning, for affirmative action, for multiculturalism. He tends to identify with victims. He tends to be against competition and against violence, but he often finds excuses for those leftists who do commit violence. He is fond of using the common catch-phrases of the left, like "racism," "sexism," "homophobia," "capitalism," "imperialism," "neocolonialism," "genocide," "social change," "social justice," "social responsibility." Maybe the best diagnostic trait of the leftist is his tendency to sympathize with the following movements: feminism, gay rights, ethnic rights, disability rights, animal rights, political correctness. Anyone who strongly sympathizes with ALL of these movements is almost certainly a leftist. [36]
230. The more dangerous leftists, that is, those who are most power-hungry, are often characterized by arrogance or by a dogmatic approach to ideology. However, the most dangerous leftists of all may be certain oversocialized types who avoid irritating displays of aggressiveness and refrain from advertising their leftism, but work quietly and unobtrusively to promote collectivist values, "enlightened" psychological techniques for socializing children, dependence of the individual on the system, and so forth. These crypto-leftists (as we may call them) approximate certain bourgeois types as far as practical action is concerned, but differ from them in psychology, ideology and motivation. The ordinary bourgeois tries to bring people under control of the system in order to protect his way of life, or he does so simply because his attitudes are conventional. The crypto-leftist tries to bring people under control of the system because he is a True Believer in a collectivistic ideology. The crypto-leftist is differentiated from the average leftist of the oversocialized type by the fact that his rebellious impulse is weaker and he is more securely socialized. He is differentiated from the ordinary well-socialized bourgeois by the fact that there is some deep lack within him that makes it necessary for him to devote himself to a cause and immerse himself in a collectivity. And maybe his (well-sublimated) drive for power is stronger than that of the average bourgeois.
FINAL NOTE
231. Throughout this article we've made imprecise statements and statements that ought to have had all sorts of qualifications and reservations attached to them; and some of our statements may be flatly false. Lack of sufficient information and the need for brevity made it impossible for us to formulate our assertions more precisely or add all the necessary qualifications. And of course in a discussion of this kind one must rely heavily on intuitive judgment, and that can sometimes be wrong. So we don't claim that this article expresses more than a crude approximation to the truth.
232. All the same, we are reasonably confident that the general outlines of the picture we have painted here are roughly correct. Just one possible weak point needs to be mentioned. We have portrayed leftism in its modern form as a phenomenon peculiar to our time and as a symptom of the disruption of the power process. But we might possibly be wrong about this. Oversocialized types who try to satisfy their drive for power by imposing their morality on everyone have certainly been around for a long time. But we THINK that the decisive role played by feelings of inferiority, low self-esteem, powerlessness, identification with victims by people who are not themselves victims, is a peculiarity of modern leftism. Identification with victims by people not themselves victims can be seen to some extent in 19th century leftism and early Christianity but as far as we can make out, symptoms of low self-esteem, etc., were not nearly so evident in these movements, or in any other movements, as they are in modern leftism. But we are not in a position to assert confidently that no such movements have existed prior to modern leftism. This is a significant question to which historians ought to give their attention.
Notes
1. (Paragraph 19) We are asserting that ALL, or even most, bullies and ruthless competitors suffer from feelings of inferiority.
2. (Paragraph 25) During the Victorian period many oversocialized people suffered from serious psychological problems as a result of repressing or trying to repress their sexual feelings. Freud apparently based his theories on people of this type. Today the focus of socialization has shifted from sex to aggression.
3. (Paragraph 27) Not necessarily including specialists in engineering or the "hard" sciences.
4. (Paragraph 28) There are many individuals of the middle and upper classes who resist some of these values, but usually their resistance is more or less covert. Such resistance appears in the mass media only to a very limited extent. The main thrust of propaganda in our society is in favor of the stated values.
The main reason why these values have become, so to speak, the official values of our society is that they are useful to the industrial system. Violence is discouraged because it disrupts the functioning of the system. Racism is discouraged because ethnic conflicts also disrupt the system, and discrimination wastes the talents of minority-group members who could be useful to the system. Poverty must be "cured" because the underclass causes problems for the system and contact with the underclass lowers the morale of the other classes. Women are encouraged to have careers because their talents are useful to the system and, more importantly, because by having regular jobs women become better integrated into the system and tied directly to it rather than to their families. This helps to weaken family solidarity. (The leaders of the system say they want to strengthen the family, but they really mean is that they want the family to serve as an effective tool for socializing children in accord with the needs of the system. We argue in paragraphs 51, 52 that the system cannot afford to let the family or other small-scale social groups be strong or autonomous.)
5. (Paragraph 42) It may be argued that the majority of people don't want to make their own decisions but want leaders to do their thinking for them. There is an element of truth in this. People like to make their own decisions in small matters, but making decisions on difficult, fundamental questions requires facing up to psychological conflict, and most people hate psychological conflict. Hence they tend to lean on others in making difficult decisions. But it does not follow that they like to have decisions imposed upon them without having any opportunity to influence those decisions. The majority of people are natural followers, not leaders, but they like to have direct personal access to their leaders, they want to be able to influence the leaders and participate to some extent in making even the difficult decisions. At least to that degree they need autonomy.
6. (Paragraph 44) Some of the symptoms listed are similar to those shown by caged animals.
To explain how these symptoms arise from deprivation with respect to the power process:
Common-sense understanding of human nature tells one that lack of goals whose attainment requires effort leads to boredom and that boredom, long continued, often leads eventually to depression. Failure to attain goals leads to frustration and lowering of self-esteem. Frustration leads to anger, anger to aggression, often in the form of spouse or child abuse. It has been shown that long-continued frustration commonly leads to depression and that depression tends to cause guilt, sleep disorders, eating disorders and bad feelings about oneself. Those who are tending toward depression seek pleasure as an antidote; hence insatiable hedonism and excessive sex, with perversions as a means of getting new kicks. Boredom too tends to cause excessive pleasure-seeking since, lacking other goals, people often use pleasure as a goal. See accompanying diagram.
The foregoing is a simplification. Reality is more complex, and of course, deprivation with respect to the power process is not the ONLY cause of the symptoms described.
By the way, when we mention depression we do not necessarily mean depression that is severe enough to be treated by a psychiatrist. Often only mild forms of depression are involved. And when we speak of goals we do not necessarily mean long-term, thought-out goals. For many or most people through much of human history, the goals of a hand-to-mouth existence (merely providing oneself and one's family with food from day to day) have been quite sufficient.
7. (Paragraph 52) A partial exception may be made for a few passive, inward-looking groups, such as the Amish, which have little effect on the wider society. Apart from these, some genuine small-scale communities do exist in America today. For instance, youth gangs and "cults." Everyone regards them as dangerous, and so they are, because the members of these groups are loyal primarily to one another rather than to the system, hence the system cannot control them.
Or take the gypsies. The gypsies commonly get away with theft and fraud because their loyalties are such that they can always get other gypsies to give testimony that "proves" their innocence. Obviously the system would be in serious trouble if too many people belonged to such groups.
Some of the early-20th century Chinese thinkers who were concerned with modernizing China recognized the necessity breaking down small-scale social groups such as the family: "(According to Sun Yat-sen) the Chinese people needed a new surge of patriotism, which would lead to a transfer of loyalty from the family to the state.... (According to Li Huang) traditional attachments, particularly to the family had to be abandoned if nationalism were to develop in China." (Chester C. Tan, "Chinese Political Thought in the Twentieth Century," page 125, page 297.)
8. (Paragraph 56) Yes, we know that 19th century America had its problems, and serious ones, but for the sake of brevity we have to express ourselves in simplified terms.
9. (Paragraph 61) We leave aside the "underclass." We are speaking of the mainstream.
10. (Paragraph 62) Some social scientists, educators, "mental health" professionals and the like are doing their best to push the social drives into group 1 by trying to see to it that everyone has a satisfactory social life.
11. (Paragraphs 63, 82) Is the drive for endless material acquisition really an artificial creation of the advertising and marketing industry? Certainly there is no innate human drive for material acquisition. There have been many cultures in which people have desired little material wealth beyond what was necessary to satisfy their basic physical needs (Australian aborigines, traditional Mexican peasant culture, some African cultures). On the other hand there have also been many pre-industrial cultures in which material acquisition has played an important role. So we can't claim that today's acquisition-oriented culture is exclusively a creation of the advertising and marketing industry. But it is clear that the advertising and marketing industry has had an important part in creating that culture. The big corporations that spend millions on advertising wouldn't be spending that kind of money without solid proof that they were getting it back in increased sales. One member of FC met a sales manager a couple of years ago who was frank enough to tell him, "Our job is to make people buy things they don't want and don't need." He then described how an untrained novice could present people with the facts about a product, and make no sales at all, while a trained and experienced professional salesman would make lots of sales to the same people. This shows that people are manipulated into buying things they don't really want.
12. (Paragraph 64) The problem of purposelessness seems to have become less serious during the last 15 years or so, because people now feel less secure physically and economically than they did earlier, and the need for security provides them with a goal. But purposelessness has been replaced by frustration over the difficulty of attaining security. We emphasize the problem of purposelessness because the liberals and leftists would wish to solve our social problems by having society guarantee everyone's security; but if that could be done it would only bring back the problem of purposelessness. The real issue is not whether society provides well or poorly for people's security; the trouble is that people are dependent on the system for their security rather than having it in their own hands. This, by the way, is part of the reason why some people get worked up about the right to bear arms; possession of a gun puts that aspect of their security in their own hands.
13. (Paragraph 66) Conservatives' efforts to decrease the amount of government regulation are of little benefit to the average man. For one thing, only a fraction of the regulations can be eliminated because most regulations are necessary. For another thing, most of the deregulation affects business rather than the average individual, so that its main effect is to take power from the government and give it to private corporations. What this means for the average man is that government interference in his life is replaced by interference from big corporations, which may be permitted, for example, to dump more chemicals that get into his water supply and give him cancer. The conservatives are just taking the average man for a sucker, exploiting his resentment of Big Government to promote the power of Big Business.
14. (Paragraph 73) When someone approves of the purpose for which propaganda is being used in a given case, he generally calls it "education" or applies to it some similar euphemism. But propaganda is propaganda regardless of the purpose for which it is used.
15. (Paragraph 83) We are not expressing approval or disapproval of the Panama invasion. We only use it to illustrate a point.
16. (Paragraph 95) When the American colonies were under British rule there were fewer and less effective legal guarantees of freedom than there were after the American Constitution went into effect, yet there was more personal freedom in pre-industrial America, both before and after the War of Independence, than there was after the Industrial Revolution took hold in this country. We quote from "Violence in America: Historical and Comparative Perspectives," edited by Hugh Davis Graham and Ted Robert Gurr, Chapter 12 by Roger Lane, pages 476-478:
"The progressive heightening of standards of propriety, and with it the increasing reliance on official law enforcement (in 19th century America) ... were common to the whole society.... [T]he change in social behavior is so long term and so widespread as to suggest a connection with the most fundamental of contemporary social processes; that of industrial urbanization itself...."Massachusetts in 1835 had a population of some 660,940, 81 percent rural, overwhelmingly preindustrial and native born. It's citizens were used to considerable personal freedom. Whether teamsters, farmers or artisans, they were all accustomed to setting their own schedules, and the nature of their work made them physically independent of each other.... Individual problems, sins or even crimes, were not generally cause for wider social concern...."But the impact of the twin movements to the city and to the factory, both just gathering force in 1835, had a progressive effect on personal behavior throughout the 19th century and into the 20th. The factory demanded regularity of behavior, a life governed by obedience to the rhythms of clock and calendar, the demands of foreman and supervisor. In the city or town, the needs of living in closely packed neighborhoods inhibited many actions previously unobjectionable. Both blue- and white-collar employees in larger establishments were mutually dependent on their fellows; as one man's work fit into anther's, so one man's business was no longer his own.
"The results of the new organization of life and work were apparent by 1900, when some 76 percent of the 2,805,346 inhabitants of Massachusetts were classified as urbanites. Much violent or irregular behavior which had been tolerable in a casual, independent society was no longer acceptable in the more formalized, cooperative atmosphere of the later period.... The move to the cities had, in short, produced a more tractable, more socialized, more 'civilized' generation than its predecessors."
17. (Paragraph 117) Apologists for the system are fond of citing cases in which elections have been decided by one or two votes, but such cases are rare.
18. (Paragraph 119) "Today, in technologically advanced lands, men live very similar lives in spite of geographical, religious, and political differences. The daily lives of a Christian bank clerk in Chicago, a Buddhist bank clerk in Tokyo, and a Communist bank clerk in Moscow are far more alike than the life of any one of them is like that of any single man who lived a thousand years ago. These similarities are the result of a common technology...." L. Sprague de Camp, "The Ancient Engineers," Ballantine edition, page 17.
The lives of the three bank clerks are not IDENTICAL. Ideology does have SOME effect. But all technological societies, in order to survive, must evolve along APPROXIMATELY the same trajectory.
19. (Paragraph 123) Just think an irresponsible genetic engineer might create a lot of terrorists.
20. (Paragraph 124) For a further example of undesirable consequences of medical progress, suppose a reliable cure for cancer is discovered. Even if the treatment is too expensive to be available to any but the elite, it will greatly reduce their incentive to stop the escape of carcinogens into the environment.
21. (Paragraph 128) Since many people may find paradoxical the notion that a large number of good things can add up to a bad thing, we illustrate with an analogy. Suppose Mr. A is playing chess with Mr. B. Mr. C, a Grand Master, is looking over Mr. A's shoulder. Mr. A of course wants to win his game, so if Mr. C points out a good move for him to make, he is doing Mr. A a favor. But suppose now that Mr. C tells Mr. A how to make ALL of his moves. In each particular instance he does Mr. A a favor by showing him his best move, but by making ALL of his moves for him he spoils his game, since there is not point in Mr. A's playing the game at all if someone else makes all his moves.
The situation of modern man is analogous to that of Mr. A. The system makes an individual's life easier for him in innumerable ways, but in doing so it deprives him of control over his own fate.
22. (Paragraph 137) Here we are considering only the conflict of values within the mainstream. For the sake of simplicity we leave out of the picture "outsider" values like the idea that wild nature is more important than human economic welfare.
23. (Paragraph 137) Self-interest is not necessarily MATERIAL self-interest. It can consist in fulfillment of some psychological need, for example, by promoting one's own ideology or religion.
24. (Paragraph 139) A qualification: It is in the interest of the system to permit a certain prescribed degree of freedom in some areas. For example, economic freedom (with suitable limitations and restraints) has proved effective in promoting economic growth. But only planned, circumscribed, limited freedom is in the interest of the system. The individual must always be kept on a leash, even if the leash is sometimes long (see paragraphs 94, 97).
25. (Paragraph 143) We don't mean to suggest that the efficiency or the potential for survival of a society has always been inversely proportional to the amount of pressure or discomfort to which the society subjects people. That certainly is not the case. There is good reason to believe that many primitive societies subjected people to less pressure than European society did, but European society proved far more efficient than any primitive society and always won out in conflicts with such societies because of the advantages conferred by technology.
26. (Paragraph 147) If you think that more effective law enforcement is unequivocally good because it suppresses crime, then remember that crime as defined by the system is not necessarily what YOU would call crime. Today, smoking marijuana is a "crime," and, in some places in the U.S., so is possession of an unregistered handgun. Tomorrow, possession of ANY firearm, registered or not, may be made a crime, and the same thing may happen with disapproved methods of child-rearing, such as spanking. In some countries, expression of dissident political opinions is a crime, and there is no certainty that this will never happen in the U.S., since no constitution or political system lasts forever.
If a society needs a large, powerful law enforcement establishment, then there is something gravely wrong with that society; it must be subjecting people to severe pressures if so many refuse to follow the rules, or follow them only because forced. Many societies in the past have gotten by with little or no formal law-enforcement.
27. (Paragraph 151) To be sure, past societies have had means of influencing human behavior, but these have been primitive and of low effectiveness compared with the technological means that are now being developed.
28. (Paragraph 152) However, some psychologists have publicly expressed opinions indicating their contempt for human freedom. And the mathematician Claude Shannon was quoted in Omni (August 1987) as saying, "I visualize a time when we will be to robots what dogs are to humans, and I'm rooting for the machines."
29. (Paragraph 154) This is no science fiction! After writing paragraph 154 we came across an article in Scientific American according to which scientists are actively developing techniques for identifying possible future criminals and for treating them by a combination of biological and psychological means. Some scientists advocate compulsory application of the treatment, which may be available in the near future. (See "Seeking the Criminal Element," by W. Wayt Gibbs, Scientific American, March 1995.) Maybe you think this is OK because the treatment would be applied to those who might become violent criminals. But of course it won't stop there. Next, a treatment will be applied to those who might become drunk drivers (they endanger human life too), then perhaps to peel who spank their children, then to environmentalists who sabotage logging equipment, eventually to anyone whose behavior is inconvenient for the system.
30. (Paragraph 184) A further advantage of nature as a counter-ideal to technology is that, in many people, nature inspires the kind of reverence that is associated with religion, so that nature could perhaps be idealized on a religious basis. It is true that in many societies religion has served as a support and justification for the established order, but it is also true that religion has often provided a basis for rebellion. Thus it may be useful to introduce a religious element into the rebellion against technology, the more so because Western society today has no strong religious foundation. Religion, nowadays either is used as cheap and transparent support for narrow, short-sighted selfishness (some conservatives use it this way), or even is cynically exploited to make easy money (by many evangelists), or has degenerated into crude irrationalism (fundamentalist protestant sects, "cults"), or is simply stagnant (Catholicism, main-line Protestantism). The nearest thing to a strong, widespread, dynamic religion that the West has seen in recent times has been the quasi-religion of leftism, but leftism today is fragmented and has no clear, unified, inspiring goal.
Thus there is a religious vacuum in our society that could perhaps be filled by a religion focused on nature in opposition to technology. But it would be a mistake to try to concoct artificially a religion to fill this role. Such an invented religion would probably be a failure. Take the "Gaia" religion for example. Do its adherents REALLY believe in it or are they just play-acting? If they are just play-acting their religion will be a flop in the end.
It is probably best not to try to introduce religion into the conflict of nature vs. technology unless you REALLY believe in that religion yourself and find that it arouses a deep, strong, genuine response in many other people.
31. (Paragraph 189) Assuming that such a final push occurs. Conceivably the industrial system might be eliminated in a somewhat gradual or piecemeal fashion (see paragraphs 4, 167 and Note 4).
32. (Paragraph 193) It is even conceivable (remotely) that the revolution might consist only of a massive change of attitudes toward technology resulting in a relatively gradual and painless disintegration of the industrial system. But if this happens we'll be very lucky. It's far more probably that the transition to a nontechnological society will be very difficult and full of conflicts and disasters.
33. (Paragraph 195) The economic and technological structure of a society are far more important than its political structure in determining the way the average man lives (see paragraphs 95, 119 and Notes 16, 18).
34. (Paragraph 215) This statement refers to our particular brand of anarchism. A wide variety of social attitudes have been called "anarchist," and it may be that many who consider themselves anarchists would not accept our statement of paragraph 215. It should be noted, by the way, that there is a nonviolent anarchist movement whose members probably would not accept FC as anarchist and certainly would not approve of FC's violent methods.
35. (Paragraph 219) Many leftists are motivated also by hostility, but the hostility probably results in part from a frustrated need for power.
36. (Paragraph 229) It is important to understand that we mean someone who sympathizes with these MOVEMENTS as they exist today in our society. One who believes that women, homosexuals, etc., should have equal rights is not necessary a leftist. The feminist, gay rights, etc., movements that exist in our society have the particular ideological tone that characterizes leftism, and if one believes, for example, that women should have equal rights it does not necessarily follow that one must sympathize with the feminist movement as it exists today.
If copyright problems make it impossible for this long quotation to be printed, then please change Note 16 to read as follows:
16. (Paragraph 95) When the American colonies were under British rule there were fewer and less effective legal guarantees of freedom than there were after the American Constitution went into effect, yet there was more personal freedom in pre-industrial America, both before and after the War of Independence, than there was after the Industrial Revolution took hold in this country. In "Violence in America: Historical and Comparative Perspectives," edited by Hugh Davis Graham and Ted Robert Gurr, Chapter 12 by Roger Lane, it is explained how in pre-industrial America the average person had greater independence and autonomy than he does today, and how the process of industrialization necessarily led to the restriction of personal freedom.
-
 @ ec42c765:328c0600
2024-12-22 19:16:31
@ ec42c765:328c0600
2024-12-22 19:16:31この記事は前回の内容を把握している人向けに書いています(特にNostrエクステンション(NIP-07)導入)
手順
- 登録する画像を用意する
- 画像をweb上にアップロードする
- 絵文字セットに登録する
1. 登録する画像を用意する
以下のような方法で用意してください。
- 画像編集ソフト等を使って自分で作成する
- 絵文字作成サイトを使う(絵文字ジェネレーター、MEGAMOJI など)
- フリー画像を使う(いらすとや など)
データ量削減
Nostrでは画像をそのまま表示するクライアントが多いので、データ量が大きな画像をそのまま使うとモバイル通信時などに負担がかかります。
データ量を増やさないためにサイズやファイル形式を変更することをおすすめします。
以下は私のおすすめです。 * サイズ:正方形 128×128 ピクセル、長方形 任意の横幅×128 ピクセル * ファイル形式:webp形式(webp変換おすすめサイト toimg) * 単色、単純な画像の場合:png形式(webpにするとむしろサイズが大きくなる)
その他
- 背景透過画像
- ダークモード、ライトモード両方で見やすい色
がおすすめです。
2. 画像をweb上にアップロードする
よく分からなければ emojito からのアップロードで問題ないです。
普段使っている画像アップロード先があるならそれでも構いません。
気になる方はアップロード先を適宜選んでください。既に投稿されたカスタム絵文字の画像に対して
- 削除も差し替えもできない → emojito など
- 削除できるが差し替えはできない → Gyazo、nostrcheck.meなど
- 削除も差し替えもできる → GitHub 、セルフホスティングなど
これらは既にNostr上に投稿されたカスタム絵文字の画像を後から変更できるかどうかを指します。
どの方法でも新しく使われるカスタム絵文字を変更することは可能です。
同一のカスタム絵文字セットに同一のショートコードで別の画像を登録する形で対応できます。3. 絵文字セットに登録する
emojito から登録します。
右上のアイコン → + New emoji set から新規の絵文字セットを作成できます。


① 絵文字セット名を入力
基本的にカスタム絵文字はカスタム絵文字セットを作り、ひとまとまりにして登録します。
一度作った絵文字セットに後から絵文字を追加することもできます。
② 画像をアップロードまたは画像URLを入力
emojitoから画像をアップロードする場合、ファイル名に日本語などの2バイト文字が含まれているとアップロードがエラーになるようです。
その場合はファイル名を適当な英数字などに変更してください。
③ 絵文字のショートコードを入力
ショートコードは絵文字を呼び出す時に使用する場合があります。
他のカスタム絵文字と被っても問題ありませんが選択時に複数表示されて支障が出る可能性があります。
他と被りにくく長くなりすぎないショートコードが良いかもしれません。
ショートコードに使えるのは半角の英数字とアンダーバーのみです。
④ 追加
Add を押してもまだ作成完了にはなりません。

一度に絵文字を複数登録できます。
最後に右上の Save を押すと作成完了です。

画面が切り替わるので、右側の Options から Bookmark を選択するとそのカスタム絵文字セットを自分で使えるようになります。
既存の絵文字セットを編集するには Options から Edit を選択します。
以上です。
仕様
-
 @ a367f9eb:0633efea
2024-12-22 21:35:22
@ a367f9eb:0633efea
2024-12-22 21:35:22I’ll admit that I was wrong about Bitcoin. Perhaps in 2013. Definitely 2017. Probably in 2018-2019. And maybe even today.
Being wrong about Bitcoin is part of finally understanding it. It will test you, make you question everything, and in the words of BTC educator and privacy advocate Matt Odell, “Bitcoin will humble you”.
I’ve had my own stumbles on the way.
In a very public fashion in 2017, after years of using Bitcoin, trying to start a company with it, using it as my primary exchange vehicle between currencies, and generally being annoying about it at parties, I let out the bear.
In an article published in my own literary magazine Devolution Review in September 2017, I had a breaking point. The article was titled “Going Bearish on Bitcoin: Cryptocurrencies are the tulip mania of the 21st century”.
It was later republished in Huffington Post and across dozens of financial and crypto blogs at the time with another, more appropriate title: “Bitcoin Has Become About The Payday, Not Its Potential”.
As I laid out, my newfound bearishness had little to do with the technology itself or the promise of Bitcoin, and more to do with the cynical industry forming around it:
In the beginning, Bitcoin was something of a revolution to me. The digital currency represented everything from my rebellious youth.
It was a decentralized, denationalized, and digital currency operating outside the traditional banking and governmental system. It used tools of cryptography and connected buyers and sellers across national borders at minimal transaction costs.
…
The 21st-century version (of Tulip mania) has welcomed a plethora of slick consultants, hazy schemes dressed up as investor possibilities, and too much wishy-washy language for anything to really make sense to anyone who wants to use a digital currency to make purchases.
While I called out Bitcoin by name at the time, on reflection, I was really talking about the ICO craze, the wishy-washy consultants, and the altcoin ponzis.
What I was articulating — without knowing it — was the frame of NgU, or “numbers go up”. Rather than advocating for Bitcoin because of its uncensorability, proof-of-work, or immutability, the common mentality among newbies and the dollar-obsessed was that Bitcoin mattered because its price was a rocket ship.
And because Bitcoin was gaining in price, affinity tokens and projects that were imperfect forks of Bitcoin took off as well.
The price alone — rather than its qualities — were the reasons why you’d hear Uber drivers, finance bros, or your gym buddy mention Bitcoin. As someone who came to Bitcoin for philosophical reasons, that just sat wrong with me.
Maybe I had too many projects thrown in my face, or maybe I was too frustrated with the UX of Bitcoin apps and sites at the time. No matter what, I’ve since learned something.
I was at least somewhat wrong.
My own journey began in early 2011. One of my favorite radio programs, Free Talk Live, began interviewing guests and having discussions on the potential of Bitcoin. They tied it directly to a libertarian vision of the world: free markets, free people, and free banking. That was me, and I was in. Bitcoin was at about $5 back then (NgU).
I followed every article I could, talked about it with guests on my college radio show, and became a devoted redditor on r/Bitcoin. At that time, at least to my knowledge, there was no possible way to buy Bitcoin where I was living. Very weak.
I was probably wrong. And very wrong for not trying to acquire by mining or otherwise.
The next year, after moving to Florida, Bitcoin was a heavy topic with a friend of mine who shared the same vision (and still does, according to the Celsius bankruptcy documents). We talked about it with passionate leftists at Occupy Tampa in 2012, all the while trying to explain the ills of Keynesian central banking, and figuring out how to use Coinbase.
I began writing more about Bitcoin in 2013, writing a guide on “How to Avoid Bank Fees Using Bitcoin,” discussing its potential legalization in Germany, and interviewing Jeremy Hansen, one of the first political candidates in the U.S. to accept Bitcoin donations.
Even up until that point, I thought Bitcoin was an interesting protocol for sending and receiving money quickly, and converting it into fiat. The global connectedness of it, plus this cypherpunk mentality divorced from government control was both useful and attractive. I thought it was the perfect go-between.
But I was wrong.
When I gave my first public speech on Bitcoin in Vienna, Austria in December 2013, I had grown obsessed with Bitcoin’s adoption on dark net markets like Silk Road.
My theory, at the time, was the number and price were irrelevant. The tech was interesting, and a novel attempt. It was unlike anything before. But what was happening on the dark net markets, which I viewed as the true free market powered by Bitcoin, was even more interesting. I thought these markets would grow exponentially and anonymous commerce via BTC would become the norm.
While the price was irrelevant, it was all about buying and selling goods without permission or license.
Now I understand I was wrong.
Just because Bitcoin was this revolutionary technology that embraced pseudonymity did not mean that all commerce would decentralize as well. It did not mean that anonymous markets were intended to be the most powerful layer in the Bitcoin stack.
What I did not even anticipate is something articulated very well by noted Bitcoin OG Pierre Rochard: Bitcoin as a savings technology.
The ability to maintain long-term savings, practice self-discipline while stacking stats, and embrace a low-time preference was just not something on the mind of the Bitcoiners I knew at the time.
Perhaps I was reading into the hype while outwardly opposing it. Or perhaps I wasn’t humble enough to understand the true value proposition that many of us have learned years later.
In the years that followed, I bought and sold more times than I can count, and I did everything to integrate it into passion projects. I tried to set up a company using Bitcoin while at my university in Prague.
My business model depended on university students being technologically advanced enough to have a mobile wallet, own their keys, and be able to make transactions on a consistent basis. Even though I was surrounded by philosophically aligned people, those who would advance that to actually put Bitcoin into practice were sparse.
This is what led me to proclaim that “Technological Literacy is Doomed” in 2016.
And I was wrong again.
Indeed, since that time, the UX of Bitcoin-only applications, wallets, and supporting tech has vastly improved and onboarded millions more people than anyone thought possible. The entrepreneurship, coding excellence, and vision offered by Bitcoiners of all stripes have renewed a sense in me that this project is something built for us all — friends and enemies alike.
While many of us were likely distracted by flashy and pumpy altcoins over the years (me too, champs), most of us have returned to the Bitcoin stable.
Fast forward to today, there are entire ecosystems of creators, activists, and developers who are wholly reliant on the magic of Bitcoin’s protocol for their life and livelihood. The options are endless. The FUD is still present, but real proof of work stands powerfully against those forces.
In addition, there are now dozens of ways to use Bitcoin privately — still without custodians or intermediaries — that make it one of the most important assets for global humanity, especially in dictatorships.
This is all toward a positive arc of innovation, freedom, and pure independence. Did I see that coming? Absolutely not.
Of course, there are probably other shots you’ve missed on Bitcoin. Price predictions (ouch), the short-term inflation hedge, or the amount of institutional investment. While all of these may be erroneous predictions in the short term, we have to realize that Bitcoin is a long arc. It will outlive all of us on the planet, and it will continue in its present form for the next generation.
Being wrong about the evolution of Bitcoin is no fault, and is indeed part of the learning curve to finally understanding it all.
When your family or friends ask you about Bitcoin after your endless sessions explaining market dynamics, nodes, how mining works, and the genius of cryptographic signatures, try to accept that there is still so much we have to learn about this decentralized digital cash.
There are still some things you’ve gotten wrong about Bitcoin, and plenty more you’ll underestimate or get wrong in the future. That’s what makes it a beautiful journey. It’s a long road, but one that remains worth it.
-
 @ 9f94e6cc:f3472946
2024-11-21 18:55:12
@ 9f94e6cc:f3472946
2024-11-21 18:55:12Der Entartungswettbewerb TikTok hat die Jugend im Griff und verbrutzelt ihre Hirne. Über Reels, den Siegeszug des Hochformats und die Regeln der Viralität.
Text: Aron Morhoff
Hollywood steckt heute in der Hosentasche. 70 Prozent aller YouTube-Inhalte werden auf mobilen Endgeräten, also Smartphones, geschaut. Instagram und TikTok sind die angesagtesten Anwendungen für junge Menschen. Es gibt sie nur noch als App, und ihr Design ist für Mobiltelefone optimiert.
Einst waren Rechner und Laptops die Tools, mit denen ins Internet gegangen wurde. Auch als das Smartphone seinen Siegeszug antrat, waren die Sehgewohnheiten noch auf das Querformat ausgerichtet. Heute werden Rechner fast nur noch zum Arbeiten verwendet. Das Berieseln, die Unterhaltung, das passive Konsumieren hat sich vollständig auf die iPhones und Samsungs dieser Welt verlagert. Das Telefon hat den aufrechten Gang angenommen, kaum einer mehr hält sein Gerät waagerecht.
Homo Digitalis Erectus
Die Welt steht also Kopf. Die Form eines Mediums hat Einfluss auf den Inhalt. Marshall McLuhan formulierte das so: Das Medium selbst ist die Botschaft. Ja mei, mag sich mancher denken, doch medienanthropologisch ist diese Entwicklung durchaus eine Betrachtung wert. Ein Querformat eignet sich besser, um Landschaften, einen Raum oder eine Gruppe abzubilden. Das Hochformat entspricht grob den menschlichen Maßen von der Hüfte bis zum Kopf. Der TikTok-Tanz ist im Smartphone-Design also schon angelegt. Das Hochformat hat die Medieninhalte unserer Zeit noch narzisstischer gemacht.
Dass wir uns durch Smartphones freizügiger und enthemmter zur Schau stellen, ist bekannt. 2013 wurde „Selfie“ vom Oxford English Dictionary zum Wort des Jahres erklärt. Selfie, Selbstporträt, Selbstdarstellung.
Neu ist der Aufwand, der heute vonnöten ist, um die Aufmerksamkeitsschwelle der todamüsierten Mediengesellschaft überhaupt noch zu durchbrechen. In beängstigender Hypnose erwischt man viele Zeitgenossen inzwischen beim Doomscrollen. Das ist der Fachbegriff für das weggetretene Endloswischen und erklärt auch den Namen „Reel“: Der Begriff, im Deutschen verwandt mit „Rolle“, beschreibt die Filmrolle, von der 24 Bilder pro Sekunde auf den Projektor gewischt oder eben abgespult werden.
Länger als drei Sekunden darf ein Kurzvideo deshalb nicht mehr gehen, ohne dass etwas Aufregendes passiert. Sonst wird das Reel aus Langeweile weggewischt. Die Welt im Dopamin-Rausch. Für den Ersteller eines Videos heißt das inzwischen: Sei der lauteste, schrillste, gestörteste Marktschreier. Das Wettrennen um die Augäpfel zwingt zu extremen Formen von Clickbait.
15 Sekunden Ruhm
Das nimmt inzwischen skurrile Formen an. Das Video „Look who I found“ von Noel Robinson (geboren 2001) war im letzten Jahr einer der erfolgreichsten deutschen TikTok-Clips. Man sieht den Deutsch-Nigerianer beim Antanzen eines karikaturartig übergewichtigen Menschen. Noel wird geschubst und fällt. Daraufhin wechselt das Lied – und der fette Mann bewegt seinen Schwabbelbauch im Takt. Noel steht wieder auf, grinst, beide tanzen gemeinsam. Das dauert 15 Sekunden. Ich rate Ihnen, sich das Video einmal anzuschauen, um die Mechanismen von TikTok zu verstehen. Achten Sie alleine darauf, wie vielen Reizen (Menschenmenge, Antanzen, Sturz, Schwabbelbauch) Sie in den ersten fünf Sekunden ausgesetzt sind. Wer schaut so was? Bis dato 220 Millionen Menschen. Das ist kapitalistische Verwertungslogik im bereits verwesten Endstadium. Adorno oder Fromm hätten am Medienzeitgeist entweder ihre Freude oder mächtig zu knabbern.
Die Internet- und Smartphoneabdeckung beträgt mittlerweile fast 100 Prozent. Das Überangebot hat die Regeln geändert. Um überhaupt gesehen zu werden, muss man heute viral gehen. Was dafür inzwischen nötig ist, spricht die niedrigsten Bedürfnisse des Menschen an: Gewalt, Ekel, Sexualisierung, Schock. Die jungen Erwachsenen, die heute auf sozialen Netzwerken den Ton angeben, haben diese Mechanismen längst verinnerlicht. Wie bewusst ihnen das ist, ist fraglich. 2024 prallt eine desaströse Bildungssituation samt fehlender Medienkompetenz auf eine egomanische Jugend, die Privatsphäre nie gekannt hat und seit Kindesbeinen alles in den Äther ballert, was es festhalten kann. Man muss kein Kulturpessimist sein, um diese degenerative Dynamik, auch in ihrer Implikation für unser Zusammenleben und das psychische Wohlergehen der Generation TikTok, als beängstigend zu bezeichnen.
Aron Morhoff studierte Medienethik und ist Absolvent der Freien Akademie für Medien & Journalismus. Frühere Stationen: RT Deutsch und Nuoviso. Heute: Stichpunkt Magazin, Manova, Milosz Matuschek und seine Liveshow "Addictive Programming".
-
 @ ccc8ee23:9f3d9783
2024-12-21 06:38:47
@ ccc8ee23:9f3d9783
2024-12-21 06:38:47Chef's notes
Enjoy these Chocolate Sprinkle Cookies, a delightful combination of buttery richness, velvety chocolate, and a crunchy sprinkle finish
Details
- ⏲️ Prep time: 10 min
- 🍳 Cook time: 90 min
- 🍽️ Servings: 10
Ingredients
- Plain flour 250 grams
- Margarine 100 grams
- Butter 100 grams
- Vanilla essence 1 tsp
- Milk powder 1 tbsp
- Sugar 40 grams
- Chocolate bar - 80 grams, melted
- Chocolate sprinkles - for decoration
Directions
- Make the Dough: Combine the plain flour, margarine, butter, milk powder, sugar, and vanilla essence in a mixing bowl. Knead the mixture by hand until smooth and well combined.
- Shape and divide the dough into small balls, weighing approximately 8 grams each.
- Preheat the oven to 175°C. Arrange the dough balls on a baking tray and bake for about 30 minutes, or until the cookies are dry and fully cooked.
- Coat with Chocolate: Melt the chocolate bar using a double boiler or microwave. Once the cookies have cooled completely, dip each cookie into the melted chocolate, ensuring they are evenly coated.
- Place the coated cookies onto paper cups.
- While the chocolate coating is still wet, sprinkle chocolate sprinkles on top of each cookie.
- Allow the chocolate to dry completely, then arrange the cookies in a decorative airtight container for storage.
-
 @ ccc8ee23:9f3d9783
2024-12-21 06:03:28
@ ccc8ee23:9f3d9783
2024-12-21 06:03:28Chef's notes
Celebrating seasons🎉
Kastengel Chocolate-Dip, where the savoury richness of cheese meets the decadent sweetness of chocolate. A perfect flavours in every bite!
Details
- ⏲️ Prep time: 10 min
- 🍳 Cook time: 90 min
- 🍽️ Servings: 10
Ingredients
- Plain Flour 250 grams
- Margarine - 100 grams
- Butter 100 grams
- Egg yolk 1 pc
- Sugar 20 grams
- Grated cheese 100 grams (half for the dough, half for garnish, adjustable)
- Chocolate bar 80 grams, melted
Directions
- Make the Dough: Combine the plain flour, margarine, butter, sugar, and half of the grated cheese in a bowl. Knead the mixture with your hands until smooth and well incorporated. Roll out the dough using a rolling pin and cut into desired shapes for cookies.
- Beat the egg yolk. Brush the shaped cookies with the egg yolk mixture and sprinkle the remaining grated cheese on top.
- Bake the cookies 175’C for about 30 minutes, or until they are dry and perfectly cooked.
- Melt the chocolate bar in a double boiler or microwave until smooth.
- Dip in Chocolate: Once the cookies have cooled completely, dip both the top and bottom ends of each cookie into the melted chocolate.
- Place the dipped cookies on a wire rack or a cookie drying tray to allow the chocolate to harden and set.
- Arrange the cookies neatly in an airtight container.
-
 @ cfd4b9f7:312596aa
2024-12-22 18:00:55
@ cfd4b9f7:312596aa
2024-12-22 18:00:55The Bitcoin Lightning Network is a solution created to make Bitcoin transactions faster, cheaper, and more efficient. As more people use Bitcoin, its main network becomes slower and more expensive. The Lightning Network helps fix these problems by allowing small, everyday transactions to happen off the main Bitcoin network.
What is the Lightning Network?
The Lightning Network is like a side road for Bitcoin transactions. Instead of sending every payment on the busy main Bitcoin network, the Lightning Network uses special payment channels to handle transactions off-chain. Later, these transactions are recorded on the main Bitcoin blockchain.
This approach helps reduce traffic on the main network, making it possible to process many more transactions every second.
How Does It Work?
Here’s how the Lightning Network operates:
-
Creating a Channel: Two people open a payment channel by locking up some Bitcoin in a shared wallet.
-
Making Transactions: They can exchange Bitcoin within this channel as many times as they want, almost instantly and for a very low cost.
-
Closing the Channel: When they’re done, the final balance is sent to the Bitcoin blockchain for recording.
For example, if Alice and Bob open a payment channel with 1 Bitcoin each, they can send money back and forth many times. Only the final result is recorded on the main Bitcoin network.
**Why Use the Lightning Network? ** 1. Faster Payments: Transactions happen almost instantly.
-
Lower Costs: Small payments (like buying coffee) become affordable because the fees are very low.
-
Scalable: It can handle millions of transactions per second, unlike the main Bitcoin network, which is much slower.
-
More Private: Payments made within a channel aren’t visible on the blockchain, offering better privacy. Challenges and Problems
The Lightning Network is still improving and has some issues:
-
Complicated Setup: Setting it up can be tricky for people who aren’t tech-savvy.
-
Tied-Up Funds: You need to lock Bitcoin in a channel, which can limit how much you can spend elsewhere.
-
Risk of Centralization: Big nodes (hubs in the network) might control too much, reducing the system’s fairness.
-
Limited Adoption: More businesses, wallets, and exchanges need to start using it.
Real-World Uses
The Lightning Network is already being used for:
Small Payments: Perfect for tipping, online games, and paying for content.
Cross-Border Transfers: Makes international payments faster and cheaper.
Everyday Shopping: Some stores now accept Bitcoin through the Lightning Network.
The Future of the Lightning Network
As more people use Bitcoin, the Lightning Network could become a key tool for everyday transactions. Developers are working to make it easier to use and fix its current issues. Companies like Strike and Cash App are already using it, showing its potential to change how we use Bitcoin.
In conclusion the Lightning Network makes Bitcoin more practical for small, everyday payments. It’s faster, cheaper, and can handle more transactions. While it’s not perfect yet, its growth and improvements suggest it could become a big part of Bitcoin’s future.
-
-
 @ eac63075:b4988b48
2024-11-09 17:57:27
@ eac63075:b4988b48
2024-11-09 17:57:27Based on a recent paper that included collaboration from renowned experts such as Lynn Alden, Steve Lee, and Ren Crypto Fish, we discuss in depth how Bitcoin's consensus is built, the main risks, and the complex dynamics of protocol upgrades.
Podcast https://www.fountain.fm/episode/wbjD6ntQuvX5u2G5BccC
Presentation https://gamma.app/docs/Analyzing-Bitcoin-Consensus-Risks-in-Protocol-Upgrades-p66axxjwaa37ksn
1. Introduction to Consensus in Bitcoin
Consensus in Bitcoin is the foundation that keeps the network secure and functional, allowing users worldwide to perform transactions in a decentralized manner without the need for intermediaries. Since its launch in 2009, Bitcoin is often described as an "immutable" system designed to resist changes, and it is precisely this resistance that ensures its security and stability.
The central idea behind consensus in Bitcoin is to create a set of acceptance rules for blocks and transactions, ensuring that all network participants agree on the transaction history. This prevents "double-spending," where the same bitcoin could be used in two simultaneous transactions, something that would compromise trust in the network.
Evolution of Consensus in Bitcoin
Over the years, consensus in Bitcoin has undergone several adaptations, and the way participants agree on changes remains a delicate process. Unlike traditional systems, where changes can be imposed from the top down, Bitcoin operates in a decentralized model where any significant change needs the support of various groups of stakeholders, including miners, developers, users, and large node operators.
Moreover, the update process is extremely cautious, as hasty changes can compromise the network's security. As a result, the philosophy of "don't fix what isn't broken" prevails, with improvements happening incrementally and only after broad consensus among those involved. This model can make progress seem slow but ensures that Bitcoin remains faithful to the principles of security and decentralization.
2. Technical Components of Consensus
Bitcoin's consensus is supported by a set of technical rules that determine what is considered a valid transaction and a valid block on the network. These technical aspects ensure that all nodes—the computers that participate in the Bitcoin network—agree on the current state of the blockchain. Below are the main technical components that form the basis of the consensus.
Validation of Blocks and Transactions
The validation of blocks and transactions is the central point of consensus in Bitcoin. A block is only considered valid if it meets certain criteria, such as maximum size, transaction structure, and the solving of the "Proof of Work" problem. The proof of work, required for a block to be included in the blockchain, is a computational process that ensures the block contains significant computational effort—protecting the network against manipulation attempts.
Transactions, in turn, need to follow specific input and output rules. Each transaction includes cryptographic signatures that prove the ownership of the bitcoins sent, as well as validation scripts that verify if the transaction conditions are met. This validation system is essential for network nodes to autonomously confirm that each transaction follows the rules.
Chain Selection
Another fundamental technical issue for Bitcoin's consensus is chain selection, which becomes especially important in cases where multiple versions of the blockchain coexist, such as after a network split (fork). To decide which chain is the "true" one and should be followed, the network adopts the criterion of the highest accumulated proof of work. In other words, the chain with the highest number of valid blocks, built with the greatest computational effort, is chosen by the network as the official one.
This criterion avoids permanent splits because it encourages all nodes to follow the same main chain, reinforcing consensus.
Soft Forks vs. Hard Forks
In the consensus process, protocol changes can happen in two ways: through soft forks or hard forks. These variations affect not only the protocol update but also the implications for network users:
-
Soft Forks: These are changes that are backward compatible. Only nodes that adopt the new update will follow the new rules, but old nodes will still recognize the blocks produced with these rules as valid. This compatibility makes soft forks a safer option for updates, as it minimizes the risk of network division.
-
Hard Forks: These are updates that are not backward compatible, requiring all nodes to update to the new version or risk being separated from the main chain. Hard forks can result in the creation of a new coin, as occurred with the split between Bitcoin and Bitcoin Cash in 2017. While hard forks allow for deeper changes, they also bring significant risks of network fragmentation.
These technical components form the base of Bitcoin's security and resilience, allowing the system to remain functional and immutable without losing the necessary flexibility to evolve over time.
3. Stakeholders in Bitcoin's Consensus
Consensus in Bitcoin is not decided centrally. On the contrary, it depends on the interaction between different groups of stakeholders, each with their motivations, interests, and levels of influence. These groups play fundamental roles in how changes are implemented or rejected on the network. Below, we explore the six main stakeholders in Bitcoin's consensus.
1. Economic Nodes
Economic nodes, usually operated by exchanges, custody providers, and large companies that accept Bitcoin, exert significant influence over consensus. Because they handle large volumes of transactions and act as a connection point between the Bitcoin ecosystem and the traditional financial system, these nodes have the power to validate or reject blocks and to define which version of the software to follow in case of a fork.
Their influence is proportional to the volume of transactions they handle, and they can directly affect which chain will be seen as the main one. Their incentive is to maintain the network's stability and security to preserve its functionality and meet regulatory requirements.
2. Investors
Investors, including large institutional funds and individual Bitcoin holders, influence consensus indirectly through their impact on the asset's price. Their buying and selling actions can affect Bitcoin's value, which in turn influences the motivation of miners and other stakeholders to continue investing in the network's security and development.
Some institutional investors have agreements with custodians that may limit their ability to act in network split situations. Thus, the impact of each investor on consensus can vary based on their ownership structure and how quickly they can react to a network change.
3. Media Influencers
Media influencers, including journalists, analysts, and popular personalities on social media, have a powerful role in shaping public opinion about Bitcoin and possible updates. These influencers can help educate the public, promote debates, and bring transparency to the consensus process.
On the other hand, the impact of influencers can be double-edged: while they can clarify complex topics, they can also distort perceptions by amplifying or minimizing change proposals. This makes them a force both of support and resistance to consensus.
4. Miners
Miners are responsible for validating transactions and including blocks in the blockchain. Through computational power (hashrate), they also exert significant influence over consensus decisions. In update processes, miners often signal their support for a proposal, indicating that the new version is safe to use. However, this signaling is not always definitive, and miners can change their position if they deem it necessary.
Their incentive is to maximize returns from block rewards and transaction fees, as well as to maintain the value of investments in their specialized equipment, which are only profitable if the network remains stable.
5. Protocol Developers
Protocol developers, often called "Core Developers," are responsible for writing and maintaining Bitcoin's code. Although they do not have direct power over consensus, they possess an informal veto power since they decide which changes are included in the main client (Bitcoin Core). This group also serves as an important source of technical knowledge, helping guide decisions and inform other stakeholders.
Their incentive lies in the continuous improvement of the network, ensuring security and decentralization. Many developers are funded by grants and sponsorships, but their motivations generally include a strong ideological commitment to Bitcoin's principles.
6. Users and Application Developers
This group includes people who use Bitcoin in their daily transactions and developers who build solutions based on the network, such as wallets, exchanges, and payment platforms. Although their power in consensus is less than that of miners or economic nodes, they play an important role because they are responsible for popularizing Bitcoin's use and expanding the ecosystem.
If application developers decide not to adopt an update, this can affect compatibility and widespread acceptance. Thus, they indirectly influence consensus by deciding which version of the protocol to follow in their applications.
These stakeholders are vital to the consensus process, and each group exerts influence according to their involvement, incentives, and ability to act in situations of change. Understanding the role of each makes it clearer how consensus is formed and why it is so difficult to make significant changes to Bitcoin.
4. Mechanisms for Activating Updates in Bitcoin
For Bitcoin to evolve without compromising security and consensus, different mechanisms for activating updates have been developed over the years. These mechanisms help coordinate changes among network nodes to minimize the risk of fragmentation and ensure that updates are implemented in an orderly manner. Here, we explore some of the main methods used in Bitcoin, their advantages and disadvantages, as well as historical examples of significant updates.
Flag Day
The Flag Day mechanism is one of the simplest forms of activating changes. In it, a specific date or block is determined as the activation moment, and all nodes must be updated by that point. This method does not involve prior signaling; participants simply need to update to the new software version by the established day or block.
-
Advantages: Simplicity and predictability are the main benefits of Flag Day, as everyone knows the exact activation date.
-
Disadvantages: Inflexibility can be a problem because there is no way to adjust the schedule if a significant part of the network has not updated. This can result in network splits if a significant number of nodes are not ready for the update.
An example of Flag Day was the Pay to Script Hash (P2SH) update in 2012, which required all nodes to adopt the change to avoid compatibility issues.
BIP34 and BIP9
BIP34 introduced a more dynamic process, in which miners increase the version number in block headers to signal the update. When a predetermined percentage of the last blocks is mined with this new version, the update is automatically activated. This model later evolved with BIP9, which allowed multiple updates to be signaled simultaneously through "version bits," each corresponding to a specific change.
-
Advantages: Allows the network to activate updates gradually, giving more time for participants to adapt.
-
Disadvantages: These methods rely heavily on miner support, which means that if a sufficient number of miners do not signal the update, it can be delayed or not implemented.
BIP9 was used in the activation of SegWit (BIP141) but faced challenges because some miners did not signal their intent to activate, leading to the development of new mechanisms.
User Activated Soft Forks (UASF) and User Resisted Soft Forks (URSF)
To increase the decision-making power of ordinary users, the concept of User Activated Soft Fork (UASF) was introduced, allowing node operators, not just miners, to determine consensus for a change. In this model, nodes set a date to start rejecting blocks that are not in compliance with the new update, forcing miners to adapt or risk having their blocks rejected by the network.
URSF, in turn, is a model where nodes reject blocks that attempt to adopt a specific update, functioning as resistance against proposed changes.
-
Advantages: UASF returns decision-making power to node operators, ensuring that changes do not depend solely on miners.
-
Disadvantages: Both UASF and URSF can generate network splits, especially in cases of strong opposition among different stakeholders.
An example of UASF was the activation of SegWit in 2017, where users supported activation independently of miner signaling, which ended up forcing its adoption.
BIP8 (LOT=True)
BIP8 is an evolution of BIP9, designed to prevent miners from indefinitely blocking a change desired by the majority of users and developers. BIP8 allows setting a parameter called "lockinontimeout" (LOT) as true, which means that if the update has not been fully signaled by a certain point, it is automatically activated.
-
Advantages: Ensures that changes with broad support among users are not blocked by miners who wish to maintain the status quo.
-
Disadvantages: Can lead to network splits if miners or other important stakeholders do not support the update.
Although BIP8 with LOT=True has not yet been used in Bitcoin, it is a proposal that can be applied in future updates if necessary.
These activation mechanisms have been essential for Bitcoin's development, allowing updates that keep the network secure and functional. Each method brings its own advantages and challenges, but all share the goal of preserving consensus and network cohesion.
5. Risks and Considerations in Consensus Updates
Consensus updates in Bitcoin are complex processes that involve not only technical aspects but also political, economic, and social considerations. Due to the network's decentralized nature, each change brings with it a set of risks that need to be carefully assessed. Below, we explore some of the main challenges and future scenarios, as well as the possible impacts on stakeholders.
Network Fragility with Alternative Implementations
One of the main risks associated with consensus updates is the possibility of network fragmentation when there are alternative software implementations. If an update is implemented by a significant group of nodes but rejected by others, a network split (fork) can occur. This creates two competing chains, each with a different version of the transaction history, leading to unpredictable consequences for users and investors.
Such fragmentation weakens Bitcoin because, by dividing hashing power (computing) and coin value, it reduces network security and investor confidence. A notable example of this risk was the fork that gave rise to Bitcoin Cash in 2017 when disagreements over block size resulted in a new chain and a new asset.
Chain Splits and Impact on Stakeholders
Chain splits are a significant risk in update processes, especially in hard forks. During a hard fork, the network is split into two separate chains, each with its own set of rules. This results in the creation of a new coin and leaves users with duplicated assets on both chains. While this may seem advantageous, in the long run, these splits weaken the network and create uncertainties for investors.
Each group of stakeholders reacts differently to a chain split:
-
Institutional Investors and ETFs: Face regulatory and compliance challenges because many of these assets are managed under strict regulations. The creation of a new coin requires decisions to be made quickly to avoid potential losses, which may be hampered by regulatory constraints.
-
Miners: May be incentivized to shift their computing power to the chain that offers higher profitability, which can weaken one of the networks.
-
Economic Nodes: Such as major exchanges and custody providers, have to quickly choose which chain to support, influencing the perceived value of each network.
Such divisions can generate uncertainties and loss of value, especially for institutional investors and those who use Bitcoin as a store of value.
Regulatory Impacts and Institutional Investors
With the growing presence of institutional investors in Bitcoin, consensus changes face new compliance challenges. Bitcoin ETFs, for example, are required to follow strict rules about which assets they can include and how chain split events should be handled. The creation of a new asset or migration to a new chain can complicate these processes, creating pressure for large financial players to quickly choose a chain, affecting the stability of consensus.
Moreover, decisions regarding forks can influence the Bitcoin futures and derivatives market, affecting perception and adoption by new investors. Therefore, the need to avoid splits and maintain cohesion is crucial to attract and preserve the confidence of these investors.
Security Considerations in Soft Forks and Hard Forks
While soft forks are generally preferred in Bitcoin for their backward compatibility, they are not without risks. Soft forks can create different classes of nodes on the network (updated and non-updated), which increases operational complexity and can ultimately weaken consensus cohesion. In a network scenario with fragmentation of node classes, Bitcoin's security can be affected, as some nodes may lose part of the visibility over updated transactions or rules.
In hard forks, the security risk is even more evident because all nodes need to adopt the new update to avoid network division. Experience shows that abrupt changes can create temporary vulnerabilities, in which malicious agents try to exploit the transition to attack the network.
Bounty Claim Risks and Attack Scenarios
Another risk in consensus updates are so-called "bounty claims"—accumulated rewards that can be obtained if an attacker manages to split or deceive a part of the network. In a conflict scenario, a group of miners or nodes could be incentivized to support a new update or create an alternative version of the software to benefit from these rewards.
These risks require stakeholders to carefully assess each update and the potential vulnerabilities it may introduce. The possibility of "bounty claims" adds a layer of complexity to consensus because each interest group may see a financial opportunity in a change that, in the long term, may harm network stability.
The risks discussed above show the complexity of consensus in Bitcoin and the importance of approaching it gradually and deliberately. Updates need to consider not only technical aspects but also economic and social implications, in order to preserve Bitcoin's integrity and maintain trust among stakeholders.
6. Recommendations for the Consensus Process in Bitcoin
To ensure that protocol changes in Bitcoin are implemented safely and with broad support, it is essential that all stakeholders adopt a careful and coordinated approach. Here are strategic recommendations for evaluating, supporting, or rejecting consensus updates, considering the risks and challenges discussed earlier, along with best practices for successful implementation.
1. Careful Evaluation of Proposal Maturity
Stakeholders should rigorously assess the maturity level of a proposal before supporting its implementation. Updates that are still experimental or lack a robust technical foundation can expose the network to unnecessary risks. Ideally, change proposals should go through an extensive testing phase, have security audits, and receive review and feedback from various developers and experts.
2. Extensive Testing in Secure and Compatible Networks
Before an update is activated on the mainnet, it is essential to test it on networks like testnet and signet, and whenever possible, on other compatible networks that offer a safe and controlled environment to identify potential issues. Testing on networks like Litecoin was fundamental for the safe launch of innovations like SegWit and the Lightning Network, allowing functionalities to be validated on a lower-impact network before being implemented on Bitcoin.
The Liquid Network, developed by Blockstream, also plays an important role as an experimental network for new proposals, such as OP_CAT. By adopting these testing environments, stakeholders can mitigate risks and ensure that the update is reliable and secure before being adopted by the main network.
3. Importance of Stakeholder Engagement
The success of a consensus update strongly depends on the active participation of all stakeholders. This includes economic nodes, miners, protocol developers, investors, and end users. Lack of participation can lead to inadequate decisions or even future network splits, which would compromise Bitcoin's security and stability.
4. Key Questions for Evaluating Consensus Proposals
To assist in decision-making, each group of stakeholders should consider some key questions before supporting a consensus change:
- Does the proposal offer tangible benefits for Bitcoin's security, scalability, or usability?
- Does it maintain backward compatibility or introduce the risk of network split?
- Are the implementation requirements clear and feasible for each group involved?
- Are there clear and aligned incentives for all stakeholder groups to accept the change?
5. Coordination and Timing in Implementations
Timing is crucial. Updates with short activation windows can force a split because not all nodes and miners can update simultaneously. Changes should be planned with ample deadlines to allow all stakeholders to adjust their systems, avoiding surprises that could lead to fragmentation.
Mechanisms like soft forks are generally preferable to hard forks because they allow a smoother transition. Opting for backward-compatible updates when possible facilitates the process and ensures that nodes and miners can adapt without pressure.
6. Continuous Monitoring and Re-evaluation
After an update, it's essential to monitor the network to identify problems or side effects. This continuous process helps ensure cohesion and trust among all participants, keeping Bitcoin as a secure and robust network.
These recommendations, including the use of secure networks for extensive testing, promote a collaborative and secure environment for Bitcoin's consensus process. By adopting a deliberate and strategic approach, stakeholders can preserve Bitcoin's value as a decentralized and censorship-resistant network.
7. Conclusion
Consensus in Bitcoin is more than a set of rules; it's the foundation that sustains the network as a decentralized, secure, and reliable system. Unlike centralized systems, where decisions can be made quickly, Bitcoin requires a much more deliberate and cooperative approach, where the interests of miners, economic nodes, developers, investors, and users must be considered and harmonized. This governance model may seem slow, but it is fundamental to preserving the resilience and trust that make Bitcoin a global store of value and censorship-resistant.
Consensus updates in Bitcoin must balance the need for innovation with the preservation of the network's core principles. The development process of a proposal needs to be detailed and rigorous, going through several testing stages, such as in testnet, signet, and compatible networks like Litecoin and Liquid Network. These networks offer safe environments for proposals to be analyzed and improved before being launched on the main network.
Each proposed change must be carefully evaluated regarding its maturity, impact, backward compatibility, and support among stakeholders. The recommended key questions and appropriate timing are critical to ensure that an update is adopted without compromising network cohesion. It's also essential that the implementation process is continuously monitored and re-evaluated, allowing adjustments as necessary and minimizing the risk of instability.
By following these guidelines, Bitcoin's stakeholders can ensure that the network continues to evolve safely and robustly, maintaining user trust and further solidifying its role as one of the most resilient and innovative digital assets in the world. Ultimately, consensus in Bitcoin is not just a technical issue but a reflection of its community and the values it represents: security, decentralization, and resilience.
8. Links
Whitepaper: https://github.com/bitcoin-cap/bcap
Youtube (pt-br): https://www.youtube.com/watch?v=rARycAibl9o&list=PL-qnhF0qlSPkfhorqsREuIu4UTbF0h4zb
-
-
 @ 4dffec17:4c4cbd48
2024-12-21 23:01:44
@ 4dffec17:4c4cbd48
2024-12-21 23:01:44What Are the Risks of Cryptocurrency? While cryptocurrencies have potential, they also come with risks:
- Volatility: Prices can rise and fall drastically in short periods.
- Security Threats: Hackers can target crypto wallets and exchanges.
- Regulatory Uncertainty: Governments are still developing crypto regulations.
- Scams: Fake projects and scams are common, so caution is crucial. Before investing in or using cryptocurrencies, understanding these risks will help you make safer decisions.
Next post: What does the future hold for cryptocurrencies?
cryptocurrency
bitcon
economy
freedom
-
 @ eac63075:b4988b48
2024-10-26 22:14:19
@ eac63075:b4988b48
2024-10-26 22:14:19The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also addressing her Bill No. 3,341/2024, which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation.
https://www.fountain.fm/episode/i5YGJ9Ors3PkqAIMvNQ0
What is a CBDC?
Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency.
A prominent feature of CBDCs is their programmability. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area.
In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously.
Practical Example: The Case of DREX During the Pandemic
To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence, limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice.
To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government.
How Does China's Social Credit System Work?
Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, including financial behavior, criminal record, social interactions, and even online activities. This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans.
With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior.
Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods, or even restricted to making transactions only at stores near their home.
Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives.
In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms.
Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression.
DREX and Bill No. 3,341/2024
Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy (Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, Julia drafted her bill, PL No. 3,341/2024, which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency.
“The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.”
Risks and Individual Freedom
Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance.
EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited.
The Relationship Between DREX and Pix
The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances.
International Precedents and Resistance to CBDC
The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations.
Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning.
Bill No. 3,341/2024 and Popular Pressure
For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill.
However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom.
What’s at Stake?
Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly.
The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way.
A Call to Action
The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance.
In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values.
-
 @ a383f86d:cdb417d4
2024-12-21 12:24:47
@ a383f86d:cdb417d4
2024-12-21 12:24:4799Beta là một trong những nền tảng trực tuyến tiên tiến, mang lại những trải nghiệm mới mẻ và thú vị cho người dùng. Với thiết kế giao diện đơn giản và thân thiện, 99Beta cho phép người dùng dễ dàng truy cập và sử dụng các dịch vụ mà không gặp phải bất kỳ sự phức tạp nào. Bất kể bạn là người mới bắt đầu hay là một người sử dụng nền tảng có kinh nghiệm, 99Beta luôn đảm bảo rằng mọi thao tác sẽ được thực hiện nhanh chóng và dễ dàng. Giao diện người dùng được tối ưu hóa cho cả máy tính để bàn và thiết bị di động, mang lại sự linh hoạt tối đa và khả năng truy cập mọi lúc, mọi nơi.
Ngoài giao diện thân thiện, 99Beta còn nổi bật với tốc độ truy cập nhanh chóng và hiệu suất ổn định. Một trong những yếu tố quan trọng khi sử dụng các dịch vụ trực tuyến chính là thời gian tải và độ trễ thấp, và 99Beta đã làm rất tốt trong việc này. Nền tảng này được tối ưu hóa kỹ càng để đảm bảo rằng người dùng sẽ có thể trải nghiệm dịch vụ mà không bị gián đoạn. Kể cả khi sử dụng qua các kết nối mạng không ổn định, người dùng vẫn có thể truy cập vào nền tảng một cách mượt mà và liên tục. Với tốc độ vượt trội, 99Beta trở thành sự lựa chọn lý tưởng cho những ai tìm kiếm một nền tảng hiệu quả và đáng tin cậy. https://99beta.cc
Bảo mật là yếu tố luôn được 99Beta chú trọng và đặt lên hàng đầu. Với những lo ngại ngày càng tăng về an toàn thông tin trong môi trường trực tuyến, 99Beta đã triển khai các công nghệ mã hóa tiên tiến để bảo vệ thông tin người dùng. Tất cả các dữ liệu cá nhân, cũng như các giao dịch tài chính, đều được mã hóa một cách an toàn để ngăn chặn sự truy cập trái phép. Với các hệ thống bảo mật chặt chẽ và luôn được cập nhật, 99Beta mang lại cho người dùng sự yên tâm tuyệt đối về vấn đề bảo mật khi sử dụng nền tảng. Người dùng có thể dễ dàng thực hiện các giao dịch và chia sẻ thông tin mà không phải lo lắng về các mối nguy cơ bảo mật.
Không chỉ tập trung vào bảo mật, 99Beta còn đặc biệt chú trọng đến chất lượng dịch vụ khách hàng. Đội ngũ hỗ trợ của nền tảng này luôn sẵn sàng giúp đỡ người dùng trong mọi tình huống. Dù là các vấn đề kỹ thuật hay những thắc mắc liên quan đến tài khoản, đội ngũ hỗ trợ khách hàng luôn đáp ứng nhanh chóng và hiệu quả. Người dùng có thể liên hệ với bộ phận chăm sóc khách hàng qua nhiều kênh như chat trực tuyến, email hoặc điện thoại, đảm bảo sẽ nhận được sự hỗ trợ kịp thời, 24/7. Đây là một yếu tố quan trọng tạo nên sự tin tưởng và lòng trung thành của người dùng đối với nền tảng.
Cuối cùng, 99Beta không ngừng cải tiến và nâng cao chất lượng dịch vụ để đáp ứng nhu cầu ngày càng cao của người dùng. Nền tảng này liên tục phát triển và cập nhật các tính năng mới, từ đó mang lại cho người dùng những trải nghiệm tuyệt vời hơn. Các phản hồi của người dùng luôn được 99Beta ghi nhận và ứng dụng để cải thiện các dịch vụ, giúp nền tảng này trở nên hoàn thiện hơn theo thời gian. Với cam kết không ngừng đổi mới và sáng tạo, 99Beta chắc chắn sẽ tiếp tục phát triển mạnh mẽ và thu hút được nhiều người dùng hơn nữa trong tương lai.
Tóm lại, 99Beta là một nền tảng trực tuyến đáng tin cậy và hiệu quả, với giao diện dễ sử dụng, tốc độ nhanh chóng, bảo mật cao và dịch vụ khách hàng tận tình. Sự đổi mới liên tục và cam kết đáp ứng nhu cầu của người dùng đã giúp nền tảng này khẳng định được vị trí vững chắc trong ngành. Với những ưu điểm vượt trội, 99Beta chắc chắn sẽ là một sự lựa chọn tuyệt vời cho những ai đang tìm kiếm một nền tảng trực tuyến an toàn, tiện lợi và đáng tin cậy.
-
 @ c69b71dc:426ba763
2024-12-22 20:36:53
@ c69b71dc:426ba763
2024-12-22 20:36:53Christ Consciousness
This text invites you to explore the deeper meaning of the winter season and the birth of Christ Consciousness—beyond religion and dogma. It is about inner reflection, spiritual insight, and the connection of body, mind, and soul, inspired by the ancient symbols of light, energy, and consciousness. Here, I highlight how the symbolism that religions and biblical texts often convey in a material sense actually holds a much deeper meaning—one that can help us awaken our life energy and unlock our full potential. Christmas is far more significant than gifts, family, food, and Christmas trees.
Winter Solstice
The winter solstice marks a turning point in the annual cycle. On December 21st, the sun reaches its southernmost point, and we experience the longest night of the year. While our physical body feels the need to rest and turn inward, our psychic and astral energies unfold. Especially between December 21st and 25th, everything seems to enter a standby mode, creating space for profound reflection and spiritual renewal. During this darkest time of the year, a kind of inner birth occurs—a birth of the spirit, conceived in the deep silence of the night. It is a moment of introspection, contemplation, and realignment.

The Twelve Holy Nights: A Time for Retreat and Reflection
With the winter solstice, the Twelve Holy Nights (Rauhnächte) begin—a mystical time between the years. These days invite us to turn inward, rest, and connect with our soul. It is a time when physical relaxation and spiritual growth go hand in hand. Advent sets the stage for this phase—each lit candle symbolically represents a chakra, starting with the lower energy centers. By the fourth Advent, the light reaches our heart chakra, a place of love, peace, and connection.
Symbolism Across Different Traditions
This energy is also reflected in Judaism: the festival of Hanukkah lasts for eight days, during which a new candle is lit each day. This practice can be seen as a symbolic journey through the chakras, gradually activating and harmonizing them. Hanukkah, the Festival of Lights, stands for the liberation from material and spiritual blockages, the strengthening and activation of energy centers, and the connection to the divine. We learn that there are no separations because we are the divine.
The Sacred Flow of Life: The Claustrum and Inner Alchemy
The term "Claustrum," referring to an occult area in the brain, holds deep symbolic and physical significance. The Claustrum is located between the pineal gland and the pituitary gland and secretes a special fluid known as "Christos." This fluid flows through the spinal cord down to the sacrum. The sacrum, derived from the Latin word "sacrum," meaning "sacred," represents this "sacred oil" flow. It symbolizes an inner alchemical process: nourishing the body and soul, enhancing consciousness, and bridging the physical and spiritual realms.
Interestingly, this process is depicted in ancient myths: Santa Claus, or Saint Nicholas, descending the chimney to deliver gifts, can be interpreted as a metaphor for the Claustrum and the flow of sacred essence. The gifts represent the awakened consciousness born from this process.
The Journey of Christ Consciousness
Christ Consciousness, often symbolized by the birth of Jesus, is understood in spiritual teachings as an internal process. The fluid from the Claustrum reaches the sacrum and then ascends to activate the pineal and pituitary glands, spreading out from there. During this process, it passes through the 33 vertebrae of the spine—a reference to the age of 33 when Jesus was crucified. During the "crucifixion" of this sacred oil, it becomes "suspended" in the region of the thalamus for two to three days before illuminating the pineal and pituitary glands. This process leads to profound spiritual renewal and heightened consciousness, often referred to as the awakening of Kundalini energy.
Nutrition and Spirituality
Our diet has a direct influence on this process. Heavy, fatty, or animal-based foods can energetically dull us and block the flow of the "sacred essence." A light, plant-based diet rich in fresh juices, sprouts, and raw foods supports energy flow and spiritual growth. Animal products, drugs, and excessive fats disrupt the process. Similarly, sexual activity with orgasm during the ascent of the sacred oil interrupts the cycle, causing the sacred energy to be lost. The pineal and pituitary glands, often referred to as the seat of the soul, are associated with the production of "manna" in spiritual traditions—a substance symbolizing milk and honey. This is also linked to Joseph and Mary or the masculine and feminine. The pineal gland secretes a honey-like substance, while the pituitary gland secretes a milk-like substance. The "land flowing with milk and honey" lies within us. We are that land. The process happens within us; there is nothing to seek outside.

The Birth of Light Within Us
In the deepest darkness lies the greatest potential for new life. Through conscious reflection, mindful nutrition, and connection with our body and mind, we can celebrate the birth of light within ourselves—a gift that helps us recognize and live our true potential.
Final Thought
I thank you from the bottom of my heart for taking the time to read this piece. My wish is to inspire and encourage you—even amidst the calls of tradition—to carve out time to look inward, just as the natural cycle of life teaches us. It is an invitation to embark on the path of self-discovery, to grow, awaken, and let our inner light shine, ultimately leading to enlightenment. Step by step, day by day, month by month, and year by year, we allow ourselves to be guided by the wisdom of the cycle, unfolding in wondrous ways. I always welcome your feedback, thoughts, and reflections on this topic. Your input is invaluable to me and enriches the process of shared growth.
May your cycle be illuminated and filled with love 💛
-
 @ fa0165a0:03397073
2024-10-23 17:19:41
@ fa0165a0:03397073
2024-10-23 17:19:41Chef's notes
This recipe is for 48 buns. Total cooking time takes at least 90 minutes, but 60 minutes of that is letting the dough rest in between processing.
The baking is a simple three-step process. 1. Making the Wheat dough 2. Making and applying the filling 3. Garnishing and baking in the oven
When done: Enjoy during Fika!
PS;
-
Can be frozen and thawed in microwave for later enjoyment as well.
-
If you need unit conversion, this site may be of help: https://www.unitconverters.net/
-
Traditionally we use something we call "Pearl sugar" which is optimal, but normal sugar or sprinkles is okay too. Pearl sugar (Pärlsocker) looks like this: https://search.brave.com/images?q=p%C3%A4rlsocker
Ingredients
- 150 g butter
- 5 dl milk
- 50 g baking yeast (normal or for sweet dough)
- 1/2 teaspoon salt
- 1-1 1/2 dl sugar
- (Optional) 2 teaspoons of crushed or grounded cardamom seeds.
- 1.4 liters of wheat flour
- Filling: 50-75 g butter, room temperature
- Filling: 1/2 - 1 dl sugar
- Filling: 1 teaspoons crushed or ground cardamom and 1 teaspoons ground cinnamon (or 2 teaspoons of cinnamon)
- Garnish: 1 egg, sugar or Almond Shavings
Directions
- Melt the butter/margarine in a saucepan.
- Pour in the milk and allow the mixture to warm reach body temperature (approx. + 37 ° C).
- Dissolve the yeast in a dough bowl with the help of the salt.
- Add the 37 ° C milk/butter mixture, sugar and if you choose to the optional cardamom. (I like this option!) and just over 2/3 of the flour.
- Work the dough shiny and smooth, about 4 minutes with a machine or 8 minutes by hand.
- Add if necessary. additional flour but save at least 1 dl for baking.
- Let the dough rise covered (by a kitchen towel), about 30 minutes.
- Work the dough into the bowl and then pick it up on a floured workbench. Knead the dough smoothly. Divide the dough into 2 parts. Roll out each piece into a rectangular cake.
- Stir together the ingredients for the filling and spread it.
- Roll up and cut each roll into 24 pieces.
- Place them in paper molds or directly on baking paper with the cut surface facing up. Let them rise covered with a baking sheet, about 30 minutes.
- Brush the buns with beaten egg and sprinkle your chosen topping.
- Bake in the middle of the oven at 250 ° C, 5-8 minutes.
- Allow to cool on a wire rack under a baking sheet.
-
-
 @ 85cd42e2:0e6f2173
2024-12-22 20:06:34
@ 85cd42e2:0e6f2173
2024-12-22 20:06:34

A gold stone lay on the ground,
And very soon, it would be found.
The forest trail began to sound.
A scribe en route was wandering down.
A single sunbeam glanced over the stone
And blinded the scribe as he thumbed through his tome.
He pushed through the brush, grabbed up the stone
And stared as its crimson lettering shone.
The cryptic writing upon the stone
Was not a language he'd ever known.
The scribe was a poor man but with this new treasure
He knew he could provide for his wife forever.
He would have time to teach, write for himself,
Help his whole village to prosper in health.
Of all the dreams that welled in his chest
The thought of having children seemed best.
Packing the stone, he started back home
But he did not know that he wasn't alone.
Two boys above, sat in a tree,
Silent and thrilled, they held back their glee.
They hurried to town and told all their friends.
Word of the stone had started to spread.

Then, one evening, asleep in his cabin,
Something terrible began to happen.
A pounding sound shook the scribe's little wood door.
Out the window was someone he'd not seen before.
A fierce-looking man with cold eyes like a shark,
He shouted commands, his voice like a bark.
"Open this door, Satoshi, the scribe.
My name is Arepo. I will come inside."
Satoshi opened the door and procured a blade.
He was taken aback but was not afraid.
"I've heard, in the village, you found a gold stone,
In the east forest, near to my home.
You know the truth, as well as do I.
The gleaming gold stone should truly be mine.
Now give it to me, or I'll break all your bones.
Give it up now, and I'll leave you alone."
Satoshi, the scribe, reached down to his side,
Drew out the stone, and he cast it aside,
"The stone is mine, thief. No one would contest,
But it's clear that your strength isn't something to test.
The stone is now yours, but not by my choice,
Now listen to wisdom and heed my voice.
Theft will always lead to regret,
For an object stolen is a spiritual debt.
You gain my gold, but with it, a curse
You can never know what it's truly worth."
The man snatched the stone off the ground with such force,
He shook the whole house and scared his own horse.
He gazed at that crimson writing on gold,
And knew the stone was some magic of old.
"I have long thought that this kingdom should taper.
This stone came to me because of God's favor.
Our kingdom is wicked, foolish, and odd.
That's how I know that this stone is from God.
The people will see this, and they'll make me king.
Despite what you think, I will do the right thing."
Arepo noticed Satoshi's fair wife,
She peeked from her hiding to observe the sharp strife.
"This scribe cannot give you the life of your dreams.
If you ever desire to leave and be free,
Come to the castle and live with me."
Arepo bowed and began to depart
With the stone in his hand and hope in his heart.

The two children who told of Satoshi's great find,
Realized that they had put him in a bind.
They meant no harm by telling the tale.
Satoshi was kind. They felt they had failed.
They went to his cabin the very next day
Expecting Satoshi to be in dismay.
Satoshi was glad to see the two boys.
He offered to carve them some new wooden toys.
They cried at his kindness and turned to go 'way.
He was concerned, and he told them to stay.
"What is it, my friends, that would cause you to cry.
I won't let you leave without telling me why."
"It's our fault that your stone was stolen away.
We told all our friends after you left that day."
"Oh, little ones, don't think of me.
All that I truly love is free.
Natural beauty, a meal, loved ones, a song;
Life's true treasures can't be stolen for long.
Even without a coin to my name,
I make what I need with my hands and my brain.
Money does not make a meaningful life.
Believe it or not, it will often bring strife.
Great piles of gold always bring dragons,
Friends become scarce, and so do one's passions.
A vibrant life, pure soul, and good friends,
Thieves gain none of these things in the end.
I sleep like a babe every night,
But now Arepo must sleep with a knife.
I've had no loss. In fact, my hopes doubled.
It's that crimson lettering that's causing me trouble.
I wrote it all down, for I love to write.
I've never seen a language the like."
He showed them his scroll, mostly for fun
But the children could read it, either the one!
"That is impossible, my young friends.
I'm a master of words, and I'm at my end."
"We can both read it, clear as the day
Ask us in separate; we'll tell you the same."
"That won't be needed, go on my friends.
Tell me what's written. Please don't pretend."
"This stone was enchanted by the Greatest of Mages.
Passed through the gate at the top of Mount Aegis.
Hidden from merchants, priests, and sages
As a guide to land free from theft or invasions.
It is obscure to those who would take it,
Revealing itself to those able to make it.
This cypher will guide you to that strange land.
Pass through the gate, but leave what's in hand."
Satoshi knew then that the gold he had tossed
Was only a vessel for knowledge t'was lost.
He set his resolve that very same day
To go to this place and pass through the gate.

Arepo became mighty; he ruled for ages.
The stone gave power over peasants and patrons.
He had fastened the stone to a staff and ruled all,
From ocean to ocean, never to fall.
Even Satoshi's precious wife,
Had left him to be with Arepo for life.
The stone had more power than he could imagine.
He cherished and studied its magic with passion.
Courts of wise men, prophets, and sages
Couldn't decipher the magic stone phrases.
He fashioned the stone from his staff to a crown.
Its power was fame, known the world 'round.
Arepo brought peace but insisted with patience
That all of the people give homage with payments.
The king's court was so grand the fees drained from the fiefdom.
The people had peace, but the king took their freedom.
Till one fateful day, his power declined.
All of the poor had stopped paying their fines.\ \ He went out to find them, to punish them all.
In many villages, there was no one at all.
He began to hear whispers among all his pages,
Many had fled to a different nation.
"Who could steal half my kingdom in such little time?
Don't they know that my rule is divine?"
At night, he was restless, and to his surprise,
Came nightmares of Satoshi's haunting eyes.
"This is the doing of Satoshi. I feel it inside.
More than my people, it's him I must find."

Arepo summoned the people of the desert,
They were the most feared trackers ever.
Arepo sent them to the kingdom's corners
And offered a bounty for Satoshi, the reformer.
While they never found the scorned scribe,
They tracked the path that he took to hide.
They drew Arepo an expert map to the Black Gate of the Immortal.
They wouldn't cross that strange gate, for a spell was upon the portal.
Arepo began planning a great expedition.
There was no stopping his inquisition.
He needed more funds from his dwindling population.
If he couldn't get taxes, he'd just have to make them.
He used the stone to replicate gold coins,
He gathered a band that made a great noise.
With armies and journeymen, women, and cases
He made his way over to scale up Mount Aegis.
The rivers were wide, and the mountains were tall.
The plains were vast, from winter to fall.
Day by day, Arepo's army would shrink.
"This isn't a problem," Arepo would think.
He made more gold to double their wages
Surely, they'd stay now. The pay was outrageous.

Arepo's army continued to leave.
By the time they arrived, their party was three.
One zealot believing without the king's power,
There couldn't be peace, not for an hour.
A priest believed that the stone was divine,
Given by God to his chosen ally.
The gate had a spell, and they couldn't pass by
Without leaving their greatest possession beside.
Arepo knew what he must leave behind.
He hid his crown in some rocks nearby.
The priest hesitated at the gates' mystic border,
His greatest possession was an amulet of his order.
He would not remove it and risk his grand rank.
He turned back at the magical gate.
The zealot, a dagger, a gift from the king
He wouldn't cross over defenseless, you see.
So Arepo alone passed through the gate
Ready for whatever he would find in wait.

Arepo gazed out at this alien land
And marveled at what he could not understand.
There were no castles, banners, or steeples.
About their business were disparate peoples.
Beggars, slaves, tradesmen, magicians
Worked together with no inhibitions.
The shelters were hidden all around.
There seemed no central city or town.
Marvelous, truly creative, and colorful,
Even the simplest cabins were wonderful.
All of the people were skilled but quite odd.
He learned that the name of this place was Karkon.

Arepo was hungry and needed provisions.
He had brought gold to complete his mission.
When he found merchants with food and lodging
They laughed at his gold and sent him walking.
In the land of Karkon, they use Edom to trade,
A blue crystal stone that smelled of the rain.
It couldn't be made with magic or tricks.
When it was stolen, it shrank to a blip.
Willingly given, Edom must be.
Not one bit was given for free.
It weighed but an ounce and was quite hard to earn.
A way to create it, Arepo could not learn.
Edom had been made by hermit mages.
That cultivated their magic through ages.
They were called the Sons of Light.
Despite their might, they did not fight.
They captured lightning with practice and patience,
Transmuted the light into something to trade with.
The land was transformed by what they had made.
Honest work was the only way to a day's wage.
Governments could not confiscate from their patrons.
War had to be funded by people's own wages.
Violence helped little in taking from others
So all work together, one with another.
All did contribute, and with less corruption
They built and they built, almost no interruption.

So Arepo worked on a farm for some time.
He knew he'd need Edom if Satoshi he'd find.

He learned in Karkon that there was no king,
But there was a clairvoyant who knew many things.
He lived in a grove, known for despair.
Arepo set out to meet him there.
When Arepo found him, he was chilled to the bone.
The wise man lived like a dog all alone.
He was cloaked in wool, with eyes of red.
Arepo approached with a great deal of dread.
"My name-"
"You are Arepo. I know who you are.
I know you have traveled exceptionally far.
You come in search of Satoshi, the scribe.
He's a man that the lowly can't find.
He is the keeper, the keeper of gates.
If you plan to catch him, then it is up to the fates."
"Surely you know the place that he stays.
Please, do not send me away in dismay."
"To go to Satoshi would take you a lifetime,
But you dare to ask twice, so I'll give you a lifeline.
If you are sincere, and you call him by name
He may appear despite your great shame." \ \ Arepo departed deeper into the grove.
He schemed and thought through all magic he'd known.

He searched that vast land, and several a time,
Got near, but Satoshi he never could find.
After some years, his spirit was broken.
He remembered the words the clairvoyant had spoken.
He whispered, "Satoshi", at last understanding
Satoshi's magic he had no hope of matching.
As sure as the clairvoyant had told him before
A gate had appeared, like a mystical door.
It was silent as death, and from this strange portal
Satoshi stepped forth, looking less like a mortal.
Arepo wept as Satoshi stood by.
"Teach me your ways; do not cast me aside.
The first time we met, I took what was yours,
You toppled my kingdom with such little force."
Satoshi looked down with a placid gaze.
"I cannot teach you the power of gates.
It was gifted to me by one greater than I,
But I can show you what you cannot find.
If you are ready, follow me through this gate.
I will take you to your kingdom of late."

The two passed through to Arepo's old kingdom.
Arepo looked up to see who would greet them.
The land was now laden with gold all around;
Golden buildings, gold even lay on the ground.
Almost too magnificent for the eye to behold,
It occurred to Arepo that this was all of his gold.
The gold he had stockpiled, the gold that he made,
So abundant they used it for cobblestone pave.
The city was silent, abandoned by all.
There was no bustling or presence at all.
There was no music or food scent in the air.
There was no culture, market, or fair.
Gold was all that this grand city now had.
The people thought there'd be nothing to add.
All became rich, but with no one to work,
It became a golden prison for the mad to lurk.
"I did nothing at all after crossing your borders,
It was your cursed gold that brought about this order.
The power you gained from that mystical stone,
Gave you all things but left you alone.
It gave you no meaning, for you searched for me,
Instead of pursuing what could make you free.
Firstly, you must learn to love all others,
All things you have, have come from another.
Secondly, you must understand your purpose,
Without a purpose, all power is worthless.
Lastly, with unwavering stoic resolve,
Master your skill until it serves all."
They passed through the portal, back to the journey's start
With nothing in hand and gold in their hearts.

Arepo felt free now from power and fear.
Trinkets and gold brought him no cheer.
Leaving his stone in the crook of Mount Aegis,
He pursued inner power, true and courageous.
Known by many as "Arepo the Might",
He use his great strength to build something right.
Building upon a foundation of gold,
He couldn't have imagined what would unfold.
He found his wife and brought her to Karkon,
He restored many things that he once thought were gone.
He found a small village and lived a pure life,
Diligent, patient, avoiding vain strife.
He worked, and he worked until one fateful day,
He discovered work that felt like play.
He became a grandmaster, a maker of clocks.
So great was his work it left others in shock.
His clocks were so masterful they could conjure odd spells,
Some could turn back time itself.
Yet, with this new power, he made no great play
To conquer the world, he left it this way.
In the end, Arepo discovered true wealth
Was not gold or power, but life, family, and health.
-
 @ eac63075:b4988b48
2024-10-21 08:11:11
@ eac63075:b4988b48
2024-10-21 08:11:11Imagine sending a private message to a friend, only to learn that authorities could be scanning its contents without your knowledge. This isn't a scene from a dystopian novel but a potential reality under the European Union's proposed "Chat Control" measures. Aimed at combating serious crimes like child exploitation and terrorism, these proposals could significantly impact the privacy of everyday internet users. As encrypted messaging services become the norm for personal and professional communication, understanding Chat Control is essential. This article delves into what Chat Control entails, why it's being considered, and how it could affect your right to private communication.
https://www.fountain.fm/episode/coOFsst7r7mO1EP1kSzV
https://open.spotify.com/episode/0IZ6kMExfxFm4FHg5DAWT8?si=e139033865e045de
Sections:
- Introduction
- What Is Chat Control?
- Why Is the EU Pushing for Chat Control?
- The Privacy Concerns and Risks
- The Technical Debate: Encryption and Backdoors
- Global Reactions and the Debate in Europe
- Possible Consequences for Messaging Services
- What Happens Next? The Future of Chat Control
- Conclusion
What Is Chat Control?
"Chat Control" refers to a set of proposed measures by the European Union aimed at monitoring and scanning private communications on messaging platforms. The primary goal is to detect and prevent the spread of illegal content, such as child sexual abuse material (CSAM) and to combat terrorism. While the intention is to enhance security and protect vulnerable populations, these proposals have raised significant privacy concerns.
At its core, Chat Control would require messaging services to implement automated scanning technologies that can analyze the content of messages—even those that are end-to-end encrypted. This means that the private messages you send to friends, family, or colleagues could be subject to inspection by algorithms designed to detect prohibited content.
Origins of the Proposal
The initiative for Chat Control emerged from the EU's desire to strengthen its digital security infrastructure. High-profile cases of online abuse and the use of encrypted platforms by criminal organizations have prompted lawmakers to consider more invasive surveillance tactics. The European Commission has been exploring legislation that would make it mandatory for service providers to monitor communications on their platforms.
How Messaging Services Work
Most modern messaging apps, like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others), use end-to-end encryption (E2EE). This encryption ensures that only the sender and the recipient can read the messages being exchanged. Not even the service providers can access the content. This level of security is crucial for maintaining privacy in digital communications, protecting users from hackers, identity thieves, and other malicious actors.

Key Elements of Chat Control
- Automated Content Scanning: Service providers would use algorithms to scan messages for illegal content.
- Circumvention of Encryption: To scan encrypted messages, providers might need to alter their encryption methods, potentially weakening security.
- Mandatory Reporting: If illegal content is detected, providers would be required to report it to authorities.
- Broad Applicability: The measures could apply to all messaging services operating within the EU, affecting both European companies and international platforms.
Why It Matters
Understanding Chat Control is essential because it represents a significant shift in how digital privacy is handled. While combating illegal activities online is crucial, the methods proposed could set a precedent for mass surveillance and the erosion of privacy rights. Everyday users who rely on encrypted messaging for personal and professional communication might find their conversations are no longer as private as they once thought.
Why Is the EU Pushing for Chat Control?
The European Union's push for Chat Control stems from a pressing concern to protect its citizens, particularly children, from online exploitation and criminal activities. With the digital landscape becoming increasingly integral to daily life, the EU aims to strengthen its ability to combat serious crimes facilitated through online platforms.
Protecting Children and Preventing Crime
One of the primary motivations behind Chat Control is the prevention of child sexual abuse material (CSAM) circulating on the internet. Law enforcement agencies have reported a significant increase in the sharing of illegal content through private messaging services. By implementing Chat Control, the EU believes it can more effectively identify and stop perpetrators, rescue victims, and deter future crimes.
Terrorism is another critical concern. Encrypted messaging apps can be used by terrorist groups to plan and coordinate attacks without detection. The EU argues that accessing these communications could be vital in preventing such threats and ensuring public safety.
Legal Context and Legislative Drivers
The push for Chat Control is rooted in several legislative initiatives:
-
ePrivacy Directive: This directive regulates the processing of personal data and the protection of privacy in electronic communications. The EU is considering amendments that would allow for the scanning of private messages under specific circumstances.
-
Temporary Derogation: In 2021, the EU adopted a temporary regulation permitting voluntary detection of CSAM by communication services. The current proposals aim to make such measures mandatory and more comprehensive.
-
Regulation Proposals: The European Commission has proposed regulations that would require service providers to detect, report, and remove illegal content proactively. This would include the use of technologies to scan private communications.
Balancing Security and Privacy
EU officials argue that the proposed measures are a necessary response to evolving digital threats. They emphasize the importance of staying ahead of criminals who exploit technology to harm others. By implementing Chat Control, they believe law enforcement can be more effective without entirely dismantling privacy protections.
However, the EU also acknowledges the need to balance security with fundamental rights. The proposals include provisions intended to limit the scope of surveillance, such as:
-
Targeted Scanning: Focusing on specific threats rather than broad, indiscriminate monitoring.
-
Judicial Oversight: Requiring court orders or oversight for accessing private communications.
-
Data Protection Safeguards: Implementing measures to ensure that data collected is handled securely and deleted when no longer needed.

The Urgency Behind the Push
High-profile cases of online abuse and terrorism have heightened the sense of urgency among EU policymakers. Reports of increasing online grooming and the widespread distribution of illegal content have prompted calls for immediate action. The EU posits that without measures like Chat Control, these problems will continue to escalate unchecked.
Criticism and Controversy
Despite the stated intentions, the push for Chat Control has been met with significant criticism. Opponents argue that the measures could be ineffective against savvy criminals who can find alternative ways to communicate. There is also concern that such surveillance could be misused or extended beyond its original purpose.
The Privacy Concerns and Risks
While the intentions behind Chat Control focus on enhancing security and protecting vulnerable groups, the proposed measures raise significant privacy concerns. Critics argue that implementing such surveillance could infringe on fundamental rights and set a dangerous precedent for mass monitoring of private communications.
Infringement on Privacy Rights
At the heart of the debate is the right to privacy. By scanning private messages, even with automated tools, the confidentiality of personal communications is compromised. Users may no longer feel secure sharing sensitive information, fearing that their messages could be intercepted or misinterpreted by algorithms.
Erosion of End-to-End Encryption
End-to-end encryption (E2EE) is a cornerstone of digital security, ensuring that only the sender and recipient can read the messages exchanged. Chat Control could necessitate the introduction of "backdoors" or weaken encryption protocols, making it easier for unauthorized parties to access private data. This not only affects individual privacy but also exposes communications to potential cyber threats.
Concerns from Privacy Advocates
Organizations like Signal and Tutanota, which offer encrypted messaging services, have voiced strong opposition to Chat Control. They warn that undermining encryption could have far-reaching consequences:
- Security Risks: Weakening encryption makes systems more vulnerable to hacking, espionage, and cybercrime.
- Global Implications: Changes in EU regulations could influence policies worldwide, leading to a broader erosion of digital privacy.
- Ineffectiveness Against Crime: Determined criminals might resort to other, less detectable means of communication, rendering the measures ineffective while still compromising the privacy of law-abiding citizens.

Potential for Government Overreach
There is a fear that Chat Control could lead to increased surveillance beyond its original scope. Once the infrastructure for scanning private messages is in place, it could be repurposed or expanded to monitor other types of content, stifling free expression and dissent.
Real-World Implications for Users
- False Positives: Automated scanning technologies are not infallible and could mistakenly flag innocent content, leading to unwarranted scrutiny or legal consequences for users.
- Chilling Effect: Knowing that messages could be monitored might discourage people from expressing themselves freely, impacting personal relationships and societal discourse.
- Data Misuse: Collected data could be vulnerable to leaks or misuse, compromising personal and sensitive information.
Legal and Ethical Concerns
Privacy advocates also highlight potential conflicts with existing laws and ethical standards:
- Violation of Fundamental Rights: The European Convention on Human Rights and other international agreements protect the right to privacy and freedom of expression.
- Questionable Effectiveness: The ethical justification for such invasive measures is challenged if they do not significantly improve safety or if they disproportionately impact innocent users.
Opposition from Member States and Organizations
Countries like Germany and organizations such as the European Digital Rights (EDRi) have expressed opposition to Chat Control. They emphasize the need to protect digital privacy and caution against hasty legislation that could have unintended consequences.
The Technical Debate: Encryption and Backdoors
The discussion around Chat Control inevitably leads to a complex technical debate centered on encryption and the potential introduction of backdoors into secure communication systems. Understanding these concepts is crucial to grasping the full implications of the proposed measures.
What Is End-to-End Encryption (E2EE)?
End-to-end encryption is a method of secure communication that prevents third parties from accessing data while it's transferred from one end system to another. In simpler terms, only the sender and the recipient can read the messages. Even the service providers operating the messaging platforms cannot decrypt the content.
- Security Assurance: E2EE ensures that sensitive information—be it personal messages, financial details, or confidential business communications—remains private.
- Widespread Use: Popular messaging apps like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others) rely on E2EE to protect user data.
How Chat Control Affects Encryption
Implementing Chat Control as proposed would require messaging services to scan the content of messages for illegal material. To do this on encrypted platforms, providers might have to:
- Introduce Backdoors: Create a means for third parties (including the service provider or authorities) to access encrypted messages.
- Client-Side Scanning: Install software on users' devices that scans messages before they are encrypted and sent, effectively bypassing E2EE.
The Risks of Weakening Encryption
1. Compromised Security for All Users
Introducing backdoors or client-side scanning tools can create vulnerabilities:
- Exploitable Gaps: If a backdoor exists, malicious actors might find and exploit it, leading to data breaches.
- Universal Impact: Weakening encryption doesn't just affect targeted individuals; it potentially exposes all users to increased risk.
2. Undermining Trust in Digital Services
- User Confidence: Knowing that private communications could be accessed might deter people from using digital services or push them toward unregulated platforms.
- Business Implications: Companies relying on secure communications might face increased risks, affecting economic activities.
3. Ineffectiveness Against Skilled Adversaries
- Alternative Methods: Criminals might shift to other encrypted channels or develop new ways to avoid detection.
- False Sense of Security: Weakening encryption could give the impression of increased safety while adversaries adapt and continue their activities undetected.
Signal’s Response and Stance
Signal, a leading encrypted messaging service, has been vocal in its opposition to the EU's proposals:
- Refusal to Weaken Encryption: Signal's CEO Meredith Whittaker has stated that the company would rather cease operations in the EU than compromise its encryption standards.
- Advocacy for Privacy: Signal emphasizes that strong encryption is essential for protecting human rights and freedoms in the digital age.
Understanding Backdoors
A "backdoor" in encryption is an intentional weakness inserted into a system to allow authorized access to encrypted data. While intended for legitimate use by authorities, backdoors pose several problems:
- Security Vulnerabilities: They can be discovered and exploited by unauthorized parties, including hackers and foreign governments.
- Ethical Concerns: The existence of backdoors raises questions about consent and the extent to which governments should be able to access private communications.

The Slippery Slope Argument
Privacy advocates warn that introducing backdoors or mandatory scanning sets a precedent:
- Expanded Surveillance: Once in place, these measures could be extended to monitor other types of content beyond the original scope.
- Erosion of Rights: Gradual acceptance of surveillance can lead to a significant reduction in personal freedoms over time.
Potential Technological Alternatives
Some suggest that it's possible to fight illegal content without undermining encryption:
- Metadata Analysis: Focusing on patterns of communication rather than content.
- Enhanced Reporting Mechanisms: Encouraging users to report illegal content voluntarily.
- Investing in Law Enforcement Capabilities: Strengthening traditional investigative methods without compromising digital security.
The technical community largely agrees that weakening encryption is not the solution:
- Consensus on Security: Strong encryption is essential for the safety and privacy of all internet users.
- Call for Dialogue: Technologists and privacy experts advocate for collaborative approaches that address security concerns without sacrificing fundamental rights.
Global Reactions and the Debate in Europe
The proposal for Chat Control has ignited a heated debate across Europe and beyond, with various stakeholders weighing in on the potential implications for privacy, security, and fundamental rights. The reactions are mixed, reflecting differing national perspectives, political priorities, and societal values.
Support for Chat Control
Some EU member states and officials support the initiative, emphasizing the need for robust measures to combat online crime and protect citizens, especially children. They argue that:
- Enhanced Security: Mandatory scanning can help law enforcement agencies detect and prevent serious crimes.
- Responsibility of Service Providers: Companies offering communication services should play an active role in preventing their platforms from being used for illegal activities.
- Public Safety Priorities: The protection of vulnerable populations justifies the implementation of such measures, even if it means compromising some aspects of privacy.
Opposition within the EU
Several countries and organizations have voiced strong opposition to Chat Control, citing concerns over privacy rights and the potential for government overreach.
Germany
- Stance: Germany has been one of the most vocal opponents of the proposed measures.
- Reasons:
- Constitutional Concerns: The German government argues that Chat Control could violate constitutional protections of privacy and confidentiality of communications.
- Security Risks: Weakening encryption is seen as a threat to cybersecurity.
- Legal Challenges: Potential conflicts with national laws protecting personal data and communication secrecy.
Netherlands
- Recent Developments: The Dutch government decided against supporting Chat Control, emphasizing the importance of encryption for security and privacy.
- Arguments:
- Effectiveness Doubts: Skepticism about the actual effectiveness of the measures in combating crime.
- Negative Impact on Privacy: Concerns about mass surveillance and the infringement of citizens' rights.
 Table reference: Patrick Breyer - Chat Control in 23 September 2024
Table reference: Patrick Breyer - Chat Control in 23 September 2024Privacy Advocacy Groups
European Digital Rights (EDRi)
- Role: A network of civil and human rights organizations working to defend rights and freedoms in the digital environment.
- Position:
- Strong Opposition: EDRi argues that Chat Control is incompatible with fundamental rights.
- Awareness Campaigns: Engaging in public campaigns to inform citizens about the potential risks.
- Policy Engagement: Lobbying policymakers to consider alternative approaches that respect privacy.
Politicians and Activists
Patrick Breyer
- Background: A Member of the European Parliament (MEP) from Germany, representing the Pirate Party.
- Actions:
- Advocacy: Actively campaigning against Chat Control through speeches, articles, and legislative efforts.
- Public Outreach: Using social media and public events to raise awareness.
- Legal Expertise: Highlighting the legal inconsistencies and potential violations of EU law.
Global Reactions
International Organizations
- Human Rights Watch and Amnesty International: These organizations have expressed concerns about the implications for human rights, urging the EU to reconsider.
Technology Companies
- Global Tech Firms: Companies like Apple and Microsoft are monitoring the situation, as EU regulations could affect their operations and user trust.
- Industry Associations: Groups representing tech companies have issued statements highlighting the risks to innovation and competitiveness.

The Broader Debate
The controversy over Chat Control reflects a broader struggle between security interests and privacy rights in the digital age. Key points in the debate include:
- Legal Precedents: How the EU's decision might influence laws and regulations in other countries.
- Digital Sovereignty: The desire of nations to control digital spaces within their borders.
- Civil Liberties: The importance of protecting freedoms in the face of technological advancements.
Public Opinion
- Diverse Views: Surveys and public forums show a range of opinions, with some citizens prioritizing security and others valuing privacy above all.
- Awareness Levels: Many people are still unaware of the potential changes, highlighting the need for public education on the issue.
The EU is at a crossroads, facing the challenge of addressing legitimate security concerns without undermining the fundamental rights that are central to its values. The outcome of this debate will have significant implications for the future of digital privacy and the balance between security and freedom in society.
Possible Consequences for Messaging Services
The implementation of Chat Control could have significant implications for messaging services operating within the European Union. Both large platforms and smaller providers might need to adapt their technologies and policies to comply with the new regulations, potentially altering the landscape of digital communication.
Impact on Encrypted Messaging Services
Signal and Similar Platforms
-
Compliance Challenges: Encrypted messaging services like Signal rely on end-to-end encryption to secure user communications. Complying with Chat Control could force them to weaken their encryption protocols or implement client-side scanning, conflicting with their core privacy principles.
-
Operational Decisions: Some platforms may choose to limit their services in the EU or cease operations altogether rather than compromise on encryption. Signal, for instance, has indicated that it would prefer to withdraw from European markets than undermine its security features.
Potential Blocking or Limiting of Services
-
Regulatory Enforcement: Messaging services that do not comply with Chat Control regulations could face fines, legal action, or even be blocked within the EU.
-
Access Restrictions: Users in Europe might find certain services unavailable or limited in functionality if providers decide not to meet the regulatory requirements.
Effects on Smaller Providers
-
Resource Constraints: Smaller messaging services and startups may lack the resources to implement the required scanning technologies, leading to increased operational costs or forcing them out of the market.
-
Innovation Stifling: The added regulatory burden could deter new entrants, reducing competition and innovation in the messaging service sector.

User Experience and Trust
-
Privacy Concerns: Users may lose trust in messaging platforms if they know their communications are subject to scanning, leading to a decline in user engagement.
-
Migration to Unregulated Platforms: There is a risk that users might shift to less secure or unregulated services, including those operated outside the EU or on the dark web, potentially exposing them to greater risks.
Technical and Security Implications
-
Increased Vulnerabilities: Modifying encryption protocols to comply with Chat Control could introduce security flaws, making platforms more susceptible to hacking and data breaches.
-
Global Security Risks: Changes made to accommodate EU regulations might affect the global user base of these services, extending security risks beyond European borders.
Impact on Businesses and Professional Communications
-
Confidentiality Issues: Businesses that rely on secure messaging for sensitive communications may face challenges in ensuring confidentiality, affecting sectors like finance, healthcare, and legal services.
-
Compliance Complexity: Companies operating internationally will need to navigate a complex landscape of differing regulations, increasing administrative burdens.
Economic Consequences
-
Market Fragmentation: Divergent regulations could lead to a fragmented market, with different versions of services for different regions.
-
Loss of Revenue: Messaging services might experience reduced revenue due to decreased user trust and engagement or the costs associated with compliance.
Responses from Service Providers
-
Legal Challenges: Companies might pursue legal action against the regulations, citing conflicts with privacy laws and user rights.
-
Policy Advocacy: Service providers may increase lobbying efforts to influence policy decisions and promote alternatives to Chat Control.
Possible Adaptations
-
Technological Innovation: Some providers might invest in developing new technologies that can detect illegal content without compromising encryption, though the feasibility remains uncertain.
-
Transparency Measures: To maintain user trust, companies might enhance transparency about how data is handled and what measures are in place to protect privacy.
The potential consequences of Chat Control for messaging services are profound, affecting not only the companies that provide these services but also the users who rely on them daily. The balance between complying with legal requirements and maintaining user privacy and security presents a significant challenge that could reshape the digital communication landscape.
What Happens Next? The Future of Chat Control
The future of Chat Control remains uncertain as the debate continues among EU member states, policymakers, technology companies, and civil society organizations. Several factors will influence the outcome of this contentious proposal, each carrying significant implications for digital privacy, security, and the regulatory environment within the European Union.
Current Status of Legislation
-
Ongoing Negotiations: The proposed Chat Control measures are still under discussion within the European Parliament and the Council of the European Union. Amendments and revisions are being considered in response to the feedback from various stakeholders.
-
Timeline: While there is no fixed date for the final decision, the EU aims to reach a consensus to implement effective measures against online crime without undue delay.
Key Influencing Factors
1. Legal Challenges and Compliance with EU Law
-
Fundamental Rights Assessment: The proposals must be evaluated against the Charter of Fundamental Rights of the European Union, ensuring that any measures comply with rights to privacy, data protection, and freedom of expression.
-
Court Scrutiny: Potential legal challenges could arise, leading to scrutiny by the European Court of Justice (ECJ), which may impact the feasibility and legality of Chat Control.
2. Technological Feasibility
-
Development of Privacy-Preserving Technologies: Research into methods that can detect illegal content without compromising encryption is ongoing. Advances in this area could provide alternative solutions acceptable to both privacy advocates and security agencies.
-
Implementation Challenges: The practical aspects of deploying scanning technologies across various platforms and services remain complex, and technical hurdles could delay or alter the proposed measures.
3. Political Dynamics
-
Member State Positions: The differing stances of EU countries, such as Germany's opposition, play a significant role in shaping the final outcome. Consensus among member states is crucial for adopting EU-wide regulations.
-
Public Opinion and Advocacy: Growing awareness and activism around digital privacy can influence policymakers. Public campaigns and lobbying efforts may sway decisions in favor of stronger privacy protections.
4. Industry Responses
-
Negotiations with Service Providers: Ongoing dialogues between EU authorities and technology companies may lead to compromises or collaborative efforts to address concerns without fully implementing Chat Control as initially proposed.
-
Potential for Self-Regulation: Messaging services might propose self-regulatory measures to combat illegal content, aiming to demonstrate effectiveness without the need for mandatory scanning.
Possible Scenarios
Optimistic Outcome:
- Balanced Regulation: A revised proposal emerges that effectively addresses security concerns while upholding strong encryption and privacy rights, possibly through innovative technologies or targeted measures with robust oversight.
Pessimistic Outcome:
- Adoption of Strict Measures: Chat Control is implemented as initially proposed, leading to weakened encryption, reduced privacy, and potential withdrawal of services like Signal from the EU market.
Middle Ground:
- Incremental Implementation: Partial measures are adopted, focusing on voluntary cooperation with service providers and emphasizing transparency and user consent, with ongoing evaluations to assess effectiveness and impact.
How to Stay Informed and Protect Your Privacy
-
Follow Reputable Sources: Keep up with news from reliable outlets, official EU communications, and statements from privacy organizations to stay informed about developments.
-
Engage in the Dialogue: Participate in public consultations, sign petitions, or contact representatives to express your views on Chat Control and digital privacy.
-
Utilize Secure Practices: Regardless of legislative outcomes, adopting good digital hygiene—such as using strong passwords and being cautious with personal information—can enhance your online security.

The Global Perspective
-
International Implications: The EU's decision may influence global policies on encryption and surveillance, setting precedents that other countries might follow or react against.
-
Collaboration Opportunities: International cooperation on developing solutions that protect both security and privacy could emerge, fostering a more unified approach to addressing online threats.
Looking Ahead
The future of Chat Control is a critical issue that underscores the challenges of governing in the digital age. Balancing the need for security with the protection of fundamental rights is a complex task that requires careful consideration, open dialogue, and collaboration among all stakeholders.
As the situation evolves, staying informed and engaged is essential. The decisions made in the coming months will shape the digital landscape for years to come, affecting how we communicate, conduct business, and exercise our rights in an increasingly connected world.
Conclusion
The debate over Chat Control highlights a fundamental challenge in our increasingly digital world: how to protect society from genuine threats without eroding the very rights and freedoms that define it. While the intention to safeguard children and prevent crime is undeniably important, the means of achieving this through intrusive surveillance measures raise critical concerns.
Privacy is not just a personal preference but a cornerstone of democratic societies. End-to-end encryption has become an essential tool for ensuring that our personal conversations, professional communications, and sensitive data remain secure from unwanted intrusion. Weakening these protections could expose individuals and organizations to risks that far outweigh the proposed benefits.
The potential consequences of implementing Chat Control are far-reaching:
- Erosion of Trust: Users may lose confidence in digital platforms, impacting how we communicate and conduct business online.
- Security Vulnerabilities: Introducing backdoors or weakening encryption can make systems more susceptible to cyberattacks.
- Stifling Innovation: Regulatory burdens may hinder technological advancement and competitiveness in the tech industry.
- Global Implications: The EU's decisions could set precedents that influence digital policies worldwide, for better or worse.
As citizens, it's crucial to stay informed about these developments. Engage in conversations, reach out to your representatives, and advocate for solutions that respect both security needs and fundamental rights. Technology and policy can evolve together to address challenges without compromising core values.
The future of Chat Control is not yet decided, and public input can make a significant difference. By promoting open dialogue, supporting privacy-preserving innovations, and emphasizing the importance of human rights in legislation, we can work towards a digital landscape that is both safe and free.
In a world where digital communication is integral to daily life, striking the right balance between security and privacy is more important than ever. The choices made today will shape the digital environment for generations to come, determining not just how we communicate, but how we live and interact in an interconnected world.

Thank you for reading this article. We hope it has provided you with a clear understanding of Chat Control and its potential impact on your privacy and digital rights. Stay informed, stay engaged, and let's work together towards a secure and open digital future.
Read more:
- https://www.patrick-breyer.de/en/posts/chat-control/
- https://www.patrick-breyer.de/en/new-eu-push-for-chat-control-will-messenger-services-be-blocked-in-europe/
- https://edri.org/our-work/dutch-decision-puts-brakes-on-chat-control/
- https://signal.org/blog/pdfs/ndss-keynote.pdf
- https://tuta.com/blog/germany-stop-chat-control
- https://cointelegraph.com/news/signal-president-slams-revised-eu-encryption-proposal
- https://mullvad.net/en/why-privacy-matters
-
 @ c4f5e7a7:8856cac7
2024-09-27 08:20:16
@ c4f5e7a7:8856cac7
2024-09-27 08:20:16Best viewed on Habla, YakiHonne or Highlighter.
TL;DR
This article explores the links between public, community-driven data sources (such as OpenStreetMap) and private, cryptographically-owned data found on networks such as Nostr.
The following concepts are explored:
- Attestations: Users signalling to their social graph that they believe something to be true by publishing Attestations. These social proofs act as a decentralised verification system that leverages your web-of-trust.
- Proof of Place: An oracle-based system where physical letters are sent to real-world locations, confirming the corresponding digital ownership via cryptographic proofs. This binds physical locations in meatspace with their digital representations in the Nostrverse.
- Check-ins: Foursquare-style check-ins that can be verified using attestations from place owners, ensuring authenticity. This approach uses web-of-trust to validate check-ins and location ownership over time.
The goal is to leverage cryptographic ownership where necessary while preserving the open, collaborative nature of public data systems.
Open Data in a public commons has a place and should not be thrown out with the Web 2.0 bathwater.
Cognitive Dissonance
Ever since discovering Nostr in August of 2022 I've been grappling with how BTC Map - a project that helps bitcoiners find places to spend sats - should most appropriately use this new protocol.
I am assuming, dear reader, that you are somewhat familiar with Nostr - a relatively new protocol for decentralised identity and communication. If you don’t know your nsec from your npub, please take some time to read these excellent posts: Nostr is Identity for the Internet and The Power of Nostr by @max and @lyn, respectively. Nostr is so much more than a short-form social media replacement.
The social features (check-ins, reviews, etc.) that Nostr unlocks for BTC Map are clear and exciting - all your silos are indeed broken - however, something fundamental has been bothering me for a while and I think it comes down to data ownership.
For those unfamiliar, BTC Map uses OpenStreetMap (OSM) as its main geographic database. OSM is centred on the concept of a commons of objectively verifiable data that is maintained by a global community of volunteer editors; a Wikipedia for maps. There is no data ownership; the data is free (as in freedom) and anyone can edit anything. It is the data equivalent of FOSS (Free and Open Source Software) - FOSD if you will, but more commonly referred to as Open Data.
In contrast, Notes and Other Stuff on Nostr (Places in this cartographic context) are explicitly owned by the controller of the private key. These notes are free to propagate, but they are owned.
How do we reconcile the decentralised nature of Nostr, where data is cryptographically owned by individuals, with the community-managed data commons of OpenStreetMap, where no one owns the data?
Self-sovereign Identity
Before I address this coexistence question, I want to talk a little about identity as it pertains to ownership. If something is to be owned, it has to be owned by someone or something - an identity.
All identities that are not self-sovereign are, by definition, leased to you by a 3rd party. You rent your Facebook identity from Meta in exchange for your data. You rent your web domain from your DNS provider in exchange for your money.
Taken to the extreme, you rent your passport from your Government in exchange for your compliance. You are you at the pleasure of others. Where Bitcoin separates money from the state; Nostr separates identity from the state.
Or, as @nvk said recently: "Don't build your house on someone else's land.".
https://i.nostr.build/xpcCSkDg3uVw0yku.png
While we’ve had the tools for self-sovereign digital identity for decades (think PGP keys or WebAuthN), we haven't had the necessary social use cases nor the corresponding social graph to elevate these identities to the mainstream. Nostr fixes this.
Nostr is PGP for the masses and will take cryptographic identities mainstream.
Full NOSTARD?
Returning to the coexistence question: the data on OpenStreetMap isn’t directly owned by anyone, even though the physical entities the data represents might be privately owned. OSM is a data commons.
We can objectively agree on the location of a tree or a fire hydrant without needing permission to observe and record it. Sure, you could place a tree ‘on Nostr’, but why should you? Just because something can be ‘on Nostr’ doesn’t mean it should be.
https://i.nostr.build/s3So2JVAqoY4E1dI.png
There might be a dystopian future where we can't agree on what a tree is nor where it's located, but I hope we never get there. It's at this point we'll need a Wikifreedia variant of OpenStreetMap.
While integrating Nostr identities into OpenStreetMap would be valuable, the current OSM infrastructure, tools, and community already provide substantial benefits in managing this data commons without needing to go NOSTR-native - there's no need to go Full NOSTARD. H/T to @princeySOV for the original meme.
https://i.nostr.build/ot9jtM5cZtDHNKWc.png
So, how do we appropriately blend cryptographically owned data with the commons?
If a location is owned in meatspace and it's useful to signal that ownership, it should also be owned in cyberspace. Our efforts should therefore focus on entities like businesses, while allowing the commons to manage public data for as long as it can successfully mitigate the tragedy of the commons.
The remainder of this article explores how we can:
- Verify ownership of a physical place in the real world;
- Link that ownership to the corresponding digital place in cyberspace.
As a side note, I don't see private key custodianship - or, even worse, permissioned use of Places signed by another identity's key - as any more viable than the rented identities of Web 2.0.
And as we all know, the Second Law of Infodynamics (no citation!) states that:
"The total amount of sensitive information leaked will always increase over time."
This especially holds true if that data is centralised.
Not your keys, not your notes. Not your keys, not your identity.
Places and Web-of-Trust
@Arkinox has been leading the charge on the Places NIP, introducing Nostr notes (kind 37515) that represent physical locations. The draft is well-crafted, with bonus points for linking back to OSM (and other location repositories) via NIP-73 - External Content IDs (championed by @oscar of @fountain).
However, as Nostr is permissionless, authenticity poses a challenge. Just because someone claims to own a physical location on the Internet doesn’t necessarily mean they have ownership or control of that location in the real world.
Ultimately, this problem can only be solved in a decentralised way by using Web-of-Trust - using your social graph and the perspectives of trusted peers to inform your own perspective. In the context of Places, this requires your network to form a view on which digital identity (public key / npub) is truly the owner of a physical place like your local coffee shop.
This requires users to:
- Verify the owner of a Place in cyberspace is the owner of a place in meatspace.
- Signal this verification to their social graph.
Let's look at the latter idea first with the concept of Attestations ...
Attestations
A way to signal to your social graph that you believe something to be true (or false for that matter) would be by publishing an Attestation note. An Attestation note would signify to your social graph that you think something is either true or false.
Imagine you're a regular at a local coffee shop. You publish an Attestation that says the shop is real and the owner behind the Nostr public key is who they claim to be. Your friends trust you, so they start trusting the shop's digital identity too.
However, attestations applied to Places are just a single use case. The attestation concept could be more widely applied across Nostr in a variety of ways (key rotation, identity linking, etc).
Here is a recent example from @lyn that would carry more signal if it were an Attestation:
https://i.nostr.build/lZAXOEwvRIghgFY4.png
Parallels can be drawn between Attestations and transaction confirmations on the Bitcoin timechain; however, their importance to you would be weighted by clients and/or Data Vending Machines in accordance with:
- Your social graph;
- The type or subject of the content being attested and by whom;
- Your personal preferences.
They could also have a validity duration to be temporally bound, which would be particularly useful in the case of Places.
NIP-25 (Reactions) do allow for users to up/downvote notes with optional content (e.g., emojis) and could work for Attestations, but I think we need something less ambiguous and more definitive.
‘This is true’ resonates more strongly than ‘I like this.’.
https://i.nostr.build/s8NIG2kXzUCLcoax.jpg
There are similar concepts in the Web 3 / Web 5 world such as Verified Credentials by tdb. However, Nostr is the Web 3 now and so wen Attestation NIP?
https://i.nostr.build/Cb047NWyHdJ7h5Ka.jpg
That said, I have seen @utxo has been exploring ‘smart contracts’ on nostr and Attestations may just be a relatively ‘dumb’ subset of the wider concept Nostr-native scripting combined with web-of-trust.
Proof of Place
Attestations handle the signalling of your truth, but what about the initial verification itself?
We already covered how this ultimately has to be derived from your social graph, but what if there was a way to help bootstrap this web-of-trust through the use of oracles? For those unfamiliar with oracles in the digital realm, they are simply trusted purveyors of truth.
Introducing Proof of Place, an out–of-band process where an oracle (such as BTC Map) would mail - yes physically mail- a shared secret to the address of the location being claimed in cyberspace. This shared secret would be locked to the public key (npub) making the claim, which, if unlocked, would prove that the associated private key (nsec) has physical access to the location in meatspace.
One way of doing this would be to mint a 1 sat cashu ecash token locked to the npub of the claimant and mail it to them. If they are able to redeem the token then they have cryptographically proven that they have physical access to the location.
Proof of Place is really nothing more than a weighted Attestation. In a web-of-trust Nostrverse, an oracle is simply a npub (say BTC Map) that you weigh heavily for its opinion on a given topic (say Places).
In the Bitcoin world, Proof of Work anchors digital scarcity in cyberspace to physical scarcity (energy and time) in meatspace and as @Gigi says in PoW is Essential:
"A failure to understand Proof of Work, is a failure to understand Bitcoin."
In the Nostrverse, Proof of Place helps bridge the digital and physical worlds.
@Gigi also observes in Memes vs The World that:
"In Bitcoin, the map is the territory. We can infer everything we care about by looking at the map alone."
https://i.nostr.build/dOnpxfI4u7EL2v4e.png
This isn’t true for Nostr.
In the Nostrverse, the map IS NOT the territory. However, Proof of Place enables us to send cryptographic drones down into the physical territory to help us interpret our digital maps. 🤯
Check-ins
Although not a draft NIP yet, @Arkinox has also been exploring the familiar concept of Foursquare-style Check-ins on Nostr (with kind 13811 notes).
For the uninitiated, Check-ins are simply notes that signal the publisher is at a given location. These locations could be Places (in the Nostr sense) or any other given digital representation of a location for that matter (such as OSM elements) if NIP-73 - External Content IDs are used.
Of course, not everyone will be a Check-in enjoyooor as the concept will not sit well with some people’s threat models and OpSec practices.
Bringing Check-ins to Nostr is possible (as @sebastix capably shows here), but they suffer the same authenticity issues as Places. Just because I say I'm at a given location doesn't mean that I am.
Back in the Web 2.0 days, Foursquare mitigated this by relying on the GPS position of the phone running their app, but this is of course spoofable.
How should we approach Check-in verifiability in the Nostrverse? Well, just like with Places, we can use Attestations and WoT. In the context of Check-ins, an Attestation from the identity (npub) of the Place being checked-in to would be a particularly strong signal. An NFC device could be placed in a coffee shop and attest to check-ins without requiring the owner to manually intervene - I’m sure @blackcoffee and @Ben Arc could hack something together over a weekend!
Check-ins could also be used as a signal for bonafide Place ownership over time.
Summary: Trust Your Bros
So, to recap, we have:
Places: Digital representations of physical locations on Nostr.
Check-ins: Users signalling their presence at a location.
Attestations: Verifiable social proofs used to confirm ownership or the truth of a claim.
You can visualise how these three concepts combine in the diagram below:
https://i.nostr.build/Uv2Jhx5BBfA51y0K.jpg
And, as always, top right trumps bottom left! We have:
Level 0 - Trust Me Bro: Anyone can check-in anywhere. The Place might not exist or might be impersonating the real place in meatspace. The person behind the npub may not have even been there at all.
Level 1 - Definitely Maybe Somewhere: This category covers the middle-ground of ‘Maybe at a Place’ and ‘Definitely Somewhere’. In these examples, you are either self-certifying that you have checked-in at an Attested Place or you are having others attest that you have checked-in at a Place that might not even exist IRL.
Level 2 - Trust Your Bros: An Attested Check-in at an Attested Place. Your individual level of trust would be a function of the number of Attestations and how you weigh them within your own social graph.
https://i.nostr.build/HtLAiJH1uQSTmdxf.jpg
Perhaps the gold standard (or should that be the Bitcoin standard?) would be a Check-in attested by the owner of the Place, which in itself was attested by BTC Map?
Or perhaps not. Ultimately, it’s the users responsibility to determine what they trust by forming their own perspective within the Nostrverse powered by web-of-trust algorithms they control. ‘Trust Me Bro’ or ‘Trust Your Bros’ - you decide.
As we navigate the frontier of cryptographic ownership and decentralised data, it’s up to us to find the balance between preserving the Open Data commons and embracing self-sovereign digital identities.
Thanks
With thanks to Arkinox, Avi, Ben Gunn, Kieran, Blackcoffee, Sebastix, Tomek, Calle, Short Fiat, Ben Weeks and Bitcoms for helping shape my thoughts and refine content, whether you know it or not!
-
 @ c11cf5f8:4928464d
2024-12-22 08:32:06
@ c11cf5f8:4928464d
2024-12-22 08:32:06Let's hear some of your latest Bitcoin purchases, feel free to include links to the shops or merchants you bought from too.
If you missed our last thread, here are some of the items stackers recently spent their sats on.
originally posted at https://stacker.news/items/820204
-
 @ a012dc82:6458a70d
2024-12-21 01:42:26
@ a012dc82:6458a70d
2024-12-21 01:42:26Table Of Content
-
The Mysterious Unidentified Miners
-
F2pool: A Titan in the Mining Arena
-
Other Notable Players
-
The Evolution of Bitcoin Mining
-
Conclusion
-
FAQ
Since the dawn of Bitcoin, introduced to the world by the mysterious Satoshi Nakamoto, the decentralized digital currency has been a topic of intrigue and speculation. At the heart of this cryptocurrency lies the process of mining, a complex computational task that validates transactions and adds them to the blockchain. Over the years, various mining pools have emerged, each contributing to the network's security and growth. Among these, two entities stand out: the unidentified miners and the dominant F2pool. This article delves into the enigmatic world of these miners and F2pool's significant role in Bitcoin's mining history.
The Mysterious Unidentified Miners
The Bitcoin blockchain, a transparent ledger of all transactions, has processed over 800,000 blocks since its inception. Interestingly, data from the last 14 years, encompassing 99 different mining pools, reveals that unidentified miners have discovered a staggering 28.37% of the network's total blocks. These miners, shrouded in mystery, include early participants like Satoshi and others who mined Bitcoin during its nascent stages.
While the identity of these miners remains unknown, their contribution to the network is undeniable. They've unearthed a cumulative 227,800 blocks, a testament to their early belief in the potential of Bitcoin and their commitment to its growth.
F2pool: A Titan in the Mining Arena
Close on the heels of these unidentified miners is F2pool, a behemoth in the Bitcoin mining world. Since 2009, F2pool has discovered 80,364 blocks, accounting for approximately 10.01% of the total. This impressive feat places F2pool as the leading identified mining pool in Bitcoin's history.
Established in 2013, F2pool, also known as DiscusFish, is based in China and has consistently been among the top mining pools in terms of hash rate. Their dominance is not just limited to Bitcoin; they have a significant presence in the mining of other cryptocurrencies like Litecoin, Ethereum, and Zcash.
The success of F2pool can be attributed to several factors:
-
Infrastructure & Technology: F2pool has invested heavily in state-of-the-art mining equipment and infrastructure, ensuring optimal performance and minimal downtime.
-
Transparency: Unlike some other mining pools, F2pool offers a transparent fee structure and provides regular updates to its members.
-
Community Engagement: F2pool has fostered a strong community of miners, offering support, educational resources, and fostering a sense of camaraderie among its members.
Other Notable Players
While the unidentified miners and F2pool have been dominant forces, other mining pools have also made significant contributions. Antpool, for instance, ranks third overall, having mined 75,829 blocks or 9.44% of the total. Following them are Btc.com’s mining pool, Braiins Pool, and Viabtc, each with their unique contributions to the network.
It's also worth noting the contributions of now-inactive mining pools. Btc Guild, for instance, mined 32,935 blocks before shutting down in 2015. Similarly, Ghash.io, which began its operations in 2013, ceased its activities in 2016 but not before mining 23,083 blocks.
The Evolution of Bitcoin Mining
The world of Bitcoin mining has seen exponential growth. In the early days, the Bitcoin network's hashrate was a mere 948 kilohash per second (KH/s). Fast forward to today, and miners are committing an astounding 387.62 exahash per second (EH/s) to the network. This astronomical increase, amounting to over 40 trillion percent since Bitcoin's inception, underscores the rapid technological advancements and the growing interest in cryptocurrency mining.
Conclusion
The history of Bitcoin mining is a tapestry woven with tales of innovation, determination, and a belief in the transformative power of decentralized digital currencies. The contributions of the enigmatic unidentified miners and the dominance of F2pool stand as testaments to the collective efforts that have fortified the Bitcoin network over the years.
As we look to the future, it's essential to acknowledge and appreciate the pioneers and leaders of the past. Their efforts have laid the foundation for a decentralized financial future, and their legacy will undoubtedly influence the generations of miners to come.
FAQ
Who are the unidentified miners in Bitcoin's history? They are early participants in the Bitcoin network, including Satoshi Nakamoto, whose identities remain unknown. They've mined approximately 28.37% of all blocks.
What is F2pool's contribution to Bitcoin mining? F2pool has discovered 80,364 blocks since 2009, making it the leading identified mining pool in Bitcoin's history.
When was F2pool established? F2pool was established in 2013 and is based in China.
Which mining pool ranks third in Bitcoin's mining history? Antpool ranks third, having mined 75,829 blocks or 9.44% of the total.
How has the Bitcoin network's hashrate evolved over time? From an initial hashrate of 948 KH/s, it has grown to a staggering 387.62 EH/s, marking an increase of over 40 trillion percent since its inception.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 4dffec17:4c4cbd48
2024-12-21 00:49:35
@ 4dffec17:4c4cbd48
2024-12-21 00:49:35The Key Benefits of Using Cryptocurrency Cryptocurrencies offer a range of advantages:
Lower Fees: Sending money across borders is cheaper than traditional banking.
Faster Transactions: Payments are processed in minutes, regardless of location.
Privacy: Users enjoy a level of anonymity when transacting.
Global Access: Anyone with internet access can use cryptocurrencies.
These benefits make crypto attractive for people, especially in regions with unreliable financial systems.
Coming up next: Let’s look at the risks involved with cryptocurrencies.
bitcoin
cryptocurrency
-
 @ 09fbf8f3:fa3d60f0
2024-09-10 13:21:23
@ 09fbf8f3:fa3d60f0
2024-09-10 13:21:23由于gmail在中国被防火墙拦截了,无法打开,不想错过邮件通知。
通过自建ntfy接受gmail邮件通知。 怎么自建ntfy,后面再写。
2024年08月13日更新:
修改不通过添加邮件标签来标记已经发送的通知,通过Google Sheets来记录已经发送的通知。
为了不让Google Sheets文档的内容很多,导致文件变大,用脚本自动清理一个星期以前的数据。
准备工具
- Ntfy服务
- Google Script
- Google Sheets
操作步骤
- 在Ntfy后台账号,设置访问令牌。
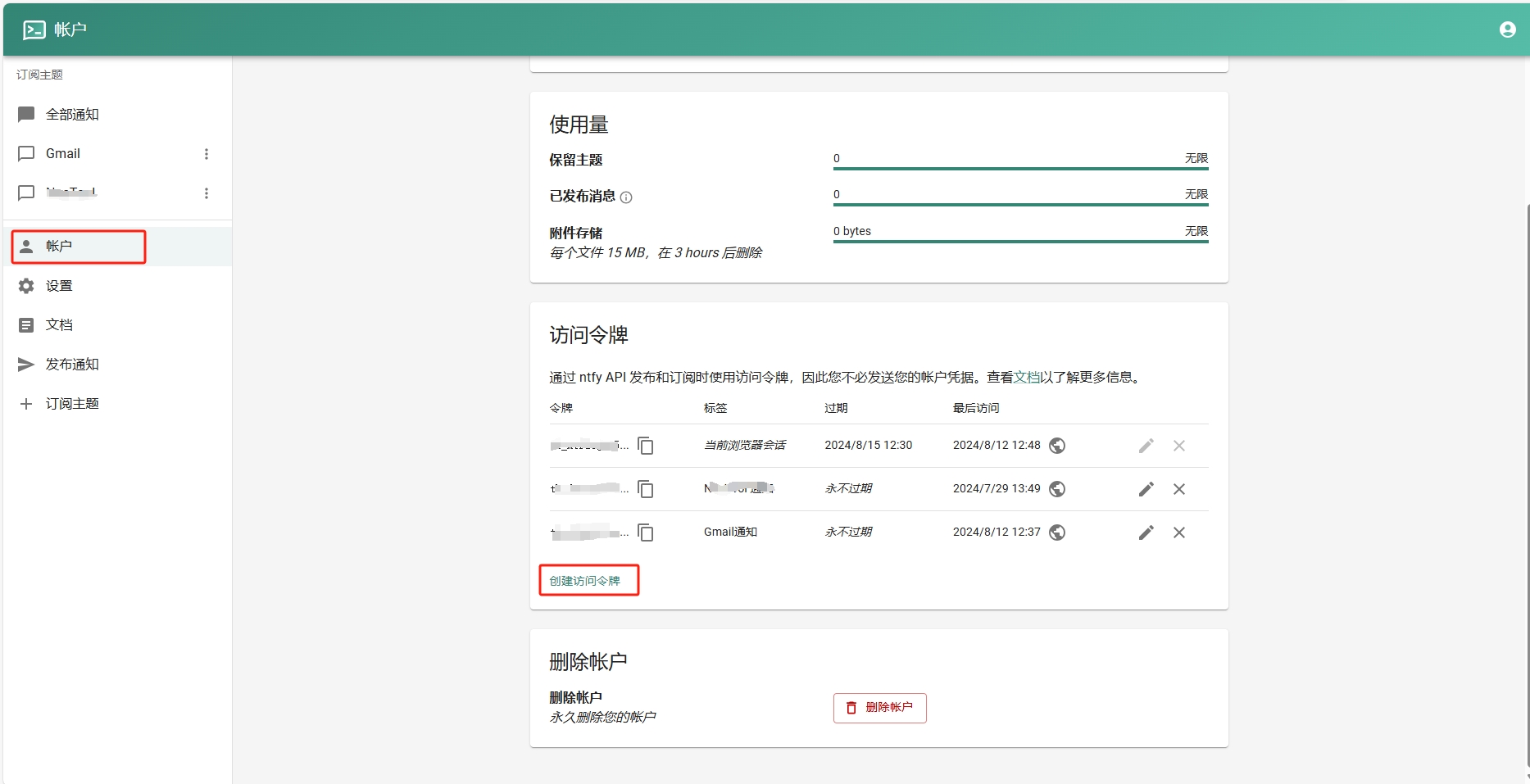
- 添加订阅主题。
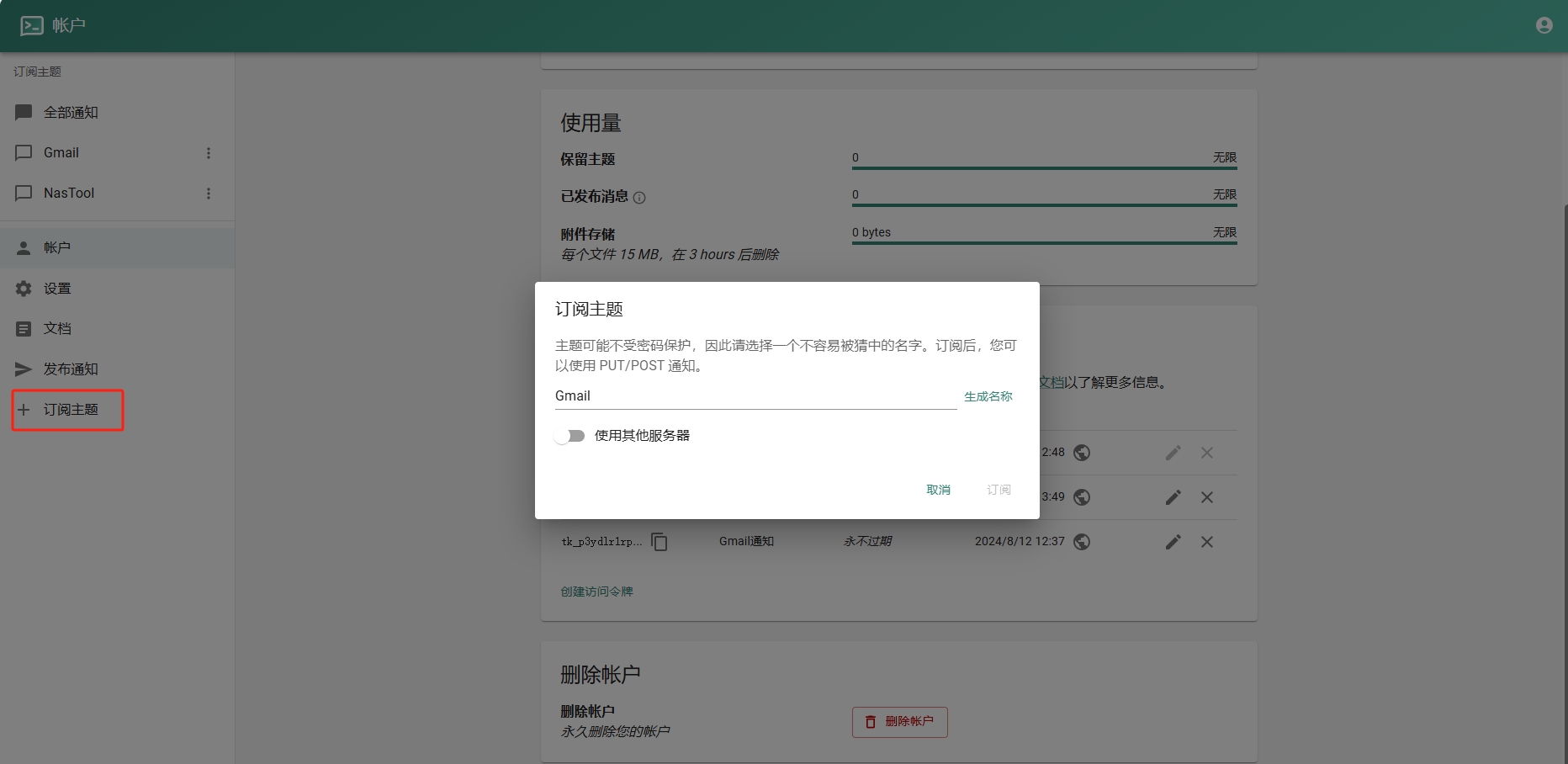
- 进入Google Sheets创建一个表格.记住id,如下图:
- 进入Google Script创建项目。填入以下代码(注意填入之前的ntfy地址和令牌):
```javascript function checkEmail() { var sheetId = "你的Google Sheets id"; // 替换为你的 Google Sheets ID var sheet = SpreadsheetApp.openById(sheetId).getActiveSheet();
// 清理一星期以前的数据 cleanOldData(sheet, 7 * 24 * 60); // 保留7天(即一周)内的数据
var sentEmails = getSentEmails(sheet);
var threads = GmailApp.search('is:unread'); Logger.log("Found threads: " + threads.length);
if (threads.length === 0) return;
threads.forEach(function(thread) { var threadId = thread.getId();
if (!sentEmails.includes(threadId)) { thread.getMessages().forEach(sendNtfyNotification); recordSentEmail(sheet, threadId); }}); }
function sendNtfyNotification(email) { if (!email) { Logger.log("Email object is undefined or null."); return; }
var message = `发件人: ${email.getFrom() || "未知发件人"} 主题: ${email.getSubject() || "无主题"}
内容: ${email.getPlainBody() || "无内容"}`;
var url = "https://你的ntfy地址/Gmail"; var options = { method: "post", payload: message, headers: { Authorization: "Bearer Ntfy的令牌" }, muteHttpExceptions: true };
try { var response = UrlFetchApp.fetch(url, options); Logger.log("Response: " + response.getContentText()); } catch (e) { Logger.log("Error: " + e.message); } }
function getSentEmails(sheet) { var data = sheet.getDataRange().getValues(); return data.map(row => row[0]); // Assuming email IDs are stored in the first column }
function recordSentEmail(sheet, threadId) { sheet.appendRow([threadId, new Date()]); }
function cleanOldData(sheet, minutes) { var now = new Date(); var thresholdDate = new Date(now.getTime() - minutes * 60 * 1000); // 获取X分钟前的时间
var data = sheet.getDataRange().getValues(); var rowsToDelete = [];
data.forEach(function(row, index) { var date = new Date(row[1]); // 假设日期保存在第二列 if (date < thresholdDate) { rowsToDelete.push(index + 1); // 存储要删除的行号 } });
// 逆序删除(从最后一行开始删除,以避免行号改变) rowsToDelete.reverse().forEach(function(row) { sheet.deleteRow(row); }); }
```
5.Google Script是有限制的不能频繁调用,可以设置五分钟调用一次。如图:
结尾
本人不会代码,以上代码都是通过chatgpt生成的。经过多次修改,刚开始会一直发送通知,后面修改后将已发送的通知放到一个“通知”的标签里。后续不会再次发送通知。
如需要发送通知后自动标记已读,可以把代码复制到chatgpt给你写。
-
 @ e356a30c:11e846f7
2024-12-20 19:21:12
@ e356a30c:11e846f7
2024-12-20 19:21:12Cryptocurrency, a digital form of money, has emerged as a revolutionary force, challenging traditional financial systems. Its decentralized nature, secure encryption, and global accessibility have captivated investors and sparked a technological revolution.
Bitcoin, the pioneer cryptocurrency, has witnessed a meteoric rise, capturing headlines with its volatile price fluctuations. This volatility, while daunting for some, underscores the transformative potential of decentralized finance (DeFi). DeFi platforms offer a range of innovative services, from lending and borrowing to decentralized exchanges, bypassing intermediaries and empowering individuals with greater control over their finances.
Beyond Bitcoin, a diverse ecosystem of cryptocurrencies is flourishing. Ethereum, for instance, enables the creation of smart contracts, self-executing agreements that automate transactions and streamline business processes. Stablecoins, pegged to stable assets like the US dollar, aim to mitigate the volatility inherent in cryptocurrencies, facilitating smoother transactions and wider adoption.
The future of cryptocurrency remains uncertain, fraught with challenges such as regulatory hurdles, security risks, and scalability issues. However, the underlying technology, blockchain, holds immense promise beyond finance. Its ability to enhance transparency, security, and efficiency has the potential to revolutionize various sectors, from supply chain management and healthcare to voting systems and identity verification.
As the world grapples with the evolving digital landscape, cryptocurrency stands poised to reshape the global financial order. Its disruptive potential, while carrying inherent risks, presents a unique opportunity to democratize finance, empower individuals, and unlock new frontiers of innovation.
Reference: * https://coinmarketcap.com/community/articles/64c8082e3f835b10be0f6596/
-
 @ a012dc82:6458a70d
2024-12-20 11:56:36
@ a012dc82:6458a70d
2024-12-20 11:56:36Table Of Content
-
Bitcoin's Journey: From Obscurity to Global Spotlight
-
Blockchain: The Backbone of Bitcoin's Success
-
The Paradox of Bitcoin's Ascendancy
-
The Intricacies of Secure Bitcoin Storage
-
The Final Word: Entrusting the Right Guardian
-
Conclusion
-
FAQ
In the digital age, where innovation is often synonymous with intangibility, Bitcoin stands as a testament to the power of decentralized finance. Born from the vision of a cashless society and the promise of financial autonomy, Bitcoin has rapidly transitioned from a theoretical concept to a tangible asset with profound global implications. However, as with any valuable asset, the question of its safekeeping becomes paramount. As Bitcoin's value skyrockets and its adoption spreads, the challenges associated with securely storing it come to the forefront. This article delves into Bitcoin's journey, the technology underpinning its success, the challenges of its storage, and the importance of entrusting its safety to the right hands. Join us as we crack the code of trust in the world of Bitcoin.
Bitcoin's Journey: From Obscurity to Global Spotlight
Bitcoin has charted an unparalleled trajectory, moving from being a fringe digital experiment to a global financial powerhouse. Its allure isn't just in its monetary value, but in the revolutionary potential it brings to the world of finance. While the market's inherent volatility can be jarring, especially during significant industry events, it's essential to recognize that such fluctuations are typical for pioneering technologies. The dot-com bubble's burst is a testament to this: groundbreaking technologies, despite initial hiccups, have historically showcased enduring value and resilience.
Blockchain: The Backbone of Bitcoin's Success
Bitcoin's rise isn't merely a result of market speculation. At its core, the underlying benefits of blockchain technology have been instrumental. Blockchain's decentralized ledger system offers transparency and security, driving an undeniable upward trend in Bitcoin's value and establishing a foundation for its long-term viability. As Bitcoin's value and global interest surge, the emphasis on its safekeeping becomes increasingly paramount.
The Paradox of Bitcoin's Ascendancy
As Bitcoin continues its meteoric rise, capturing the imagination and investment of people worldwide, its very success presents a paradox. This digital currency, once a niche concept known only to a select few, now finds itself in the global spotlight, and with this heightened attention comes a slew of challenges. The popularity and widespread adoption of Bitcoin have inadvertently made it a prime target for cyber threats and potential malfeasance. As more individuals and institutions flock to the Bitcoin ecosystem, the complexities of ensuring its safety become increasingly intricate. While there are numerous challenges that the Bitcoin community must grapple with, the issue of secure storage stands out. It's not just about protecting one's investment; it's about safeguarding the very integrity and trust that Bitcoin has built over the years. The question then arises: in an age where digital assets are becoming as valuable as physical ones, how do we ensure that Bitcoin remains both accessible and secure?
The Intricacies of Secure Bitcoin Storage
Many individuals are drawn to the Bitcoin realm with trading aspirations, aiming for significant returns. This trend is especially pronounced in developed economies. However, in emerging markets, the allure of a decentralized store of value is tangible. As a result, exchanges have become the primary gateway for many to enter the Bitcoin world. While these platforms are equipped with various security measures and are designed for trading, they often house vast amounts of Bitcoin. The challenge? These platforms, despite their security measures, aren't inherently designed for the long-term, secure storage of Bitcoin. A cursory online search about "Bitcoin exchange hacks" reveals numerous incidents, highlighting the risks of relying solely on exchanges for safeguarding one's Bitcoin assets.
The Final Word: Entrusting the Right Guardian The essence of the Bitcoin storage dilemma revolves around trust. As the ecosystem continues to evolve, both individuals and institutions must critically assess where and how they store their Bitcoin. The goal is to find a balance between trading accessibility and the security required for long-term holding. In this dynamic landscape, understanding the intricacies of Bitcoin storage and placing trust in the right guardians will be pivotal in ensuring the safety and appreciation of one's Bitcoin investments.
Conclusion
As we stand on the cusp of a financial revolution, Bitcoin's prominence in the global financial landscape is undeniable. Its meteoric rise, underpinned by the robustness of blockchain technology, has reshaped our understanding of value, trust, and decentralization. However, with great value comes the pressing responsibility of protection. The challenges of securely storing Bitcoin are not mere technical hurdles but pivotal concerns that will define its future adoption and integration. As enthusiasts, investors, and guardians of this digital gold, our collective responsibility is to ensure its safekeeping. By understanding the nuances of storage, being vigilant of potential risks, and placing our trust in reliable custodians, we can ensure that Bitcoin's promise is not just preserved but flourishes in the years to come. The journey of Bitcoin is as much about innovation as it is about trust, and as we move forward, it's this trust that will shape its legacy.
FAQ
Why is secure storage important for Bitcoin? Given its high value and digital nature, Bitcoin is a target for cyber theft. Secure storage ensures the safety of one's assets against hacks and unauthorized access.
Are exchanges safe for storing Bitcoin? While exchanges have security measures, they are primarily designed for trading. For long-term storage, dedicated Bitcoin wallets or cold storage solutions are recommended.
What is blockchain in relation to Bitcoin? Blockchain is the underlying technology of Bitcoin. It's a decentralized ledger system that records all Bitcoin transactions in a transparent and secure manner.
How can I ensure the safety of my Bitcoin investments? By understanding storage nuances, using secure wallets, regularly updating security protocols, and staying informed about potential risks.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ ac8bb9b0:70278acc
2024-12-20 18:48:36
@ ac8bb9b0:70278acc
2024-12-20 18:48:36Details
- ⏲️ Prep time: 5
- 🍳 Cook time: 10
- 🍽️ Servings: 4
Ingredients
- 1 lb large shrimp, peeled and deveined
- 1 tablespoon extra virgin olive oil
- 3 cloves garlic, chopped
- 1/4 cup white wine, dry
- 14 oz can petite diced tomatoes, drained
- 1/2 cup half and half
- 1/2 teaspoon dried oregano
- kosher salt and fresh black pepper, to taste
- 1 teaspoon lemon juice
- 1/4 cup fresh parsley, chopped
- 8 ounces angel hair pasta, whole wheat, gluten-free or high fiber
Directions
- Boil water with salt in a large pot for the pasta. Cook pasta al dente according to package directions.
- Meanwhile, season shrimp with 1/4 teaspoon salt, black pepper and oregano.
- Heat a large skillet over medium heat. Add the oil, when warm add the shrimp and garlic and cook about 2 minutes on each side.
- Add tomatoes, wine, salt and pepper and cook an additional minute.
- Remove from heat and stir in half and half. Add lemon juice and parsley and serve over pasta.
- Divide equally in 4 plates or shallow bowls.
-
 @ 6e468422:15deee93
2024-12-21 19:25:26
@ 6e468422:15deee93
2024-12-21 19:25:26We didn't hear them land on earth, nor did we see them. The spores were not visible to the naked eye. Like dust particles, they softly fell, unhindered, through our atmosphere, covering the earth. It took us a while to realize that something extraordinary was happening on our planet. In most places, the mushrooms didn't grow at all. The conditions weren't right. In some places—mostly rocky places—they grew large enough to be noticeable. People all over the world posted pictures online. "White eggs," they called them. It took a bit until botanists and mycologists took note. Most didn't realize that we were dealing with a species unknown to us.
We aren't sure who sent them. We aren't even sure if there is a "who" behind the spores. But once the first portals opened up, we learned that these mushrooms aren't just a quirk of biology. The portals were small at first—minuscule, even. Like a pinhole camera, we were able to glimpse through, but we couldn't make out much. We were only able to see colors and textures if the conditions were right. We weren't sure what we were looking at.
We still don't understand why some mushrooms open up, and some don't. Most don't. What we do know is that they like colder climates and high elevations. What we also know is that the portals don't stay open for long. Like all mushrooms, the flush only lasts for a week or two. When a portal opens, it looks like the mushroom is eating a hole into itself at first. But the hole grows, and what starts as a shimmer behind a grey film turns into a clear picture as the egg ripens. When conditions are right, portals will remain stable for up to three days. Once the fruit withers, the portal closes, and the mushroom decays.
The eggs grew bigger year over year. And with it, the portals. Soon enough, the portals were big enough to stick your finger through. And that's when things started to get weird...
-
 @ 7460b7fd:4fc4e74b
2024-09-05 08:37:48
@ 7460b7fd:4fc4e74b
2024-09-05 08:37:48请看2014年王兴的一场思维碰撞,视频27分钟开始
最后,一个当时无法解决的点:丢失
-
 @ 88dc84f5:c71164f7
2024-12-19 12:08:51
@ 88dc84f5:c71164f7
2024-12-19 12:08:51Introduction Quantum computing is a revolutionary technology that uses the principles of quantum mechanics to perform calculations that are exponentially faster and more powerful than those of classical computers. The rise of quantum computing has significant implications for cybersecurity and data protection, and in this article, we will explore what these implications are.
 The Power of Quantum Computing
Quantum computers use quantum bits or qubits, which can exist in multiple states simultaneously, allowing for an exponential increase in computing power. This means that quantum computers can perform certain calculations much faster than classical computers, which has significant implications for cybersecurity.
The Power of Quantum Computing
Quantum computers use quantum bits or qubits, which can exist in multiple states simultaneously, allowing for an exponential increase in computing power. This means that quantum computers can perform certain calculations much faster than classical computers, which has significant implications for cybersecurity.
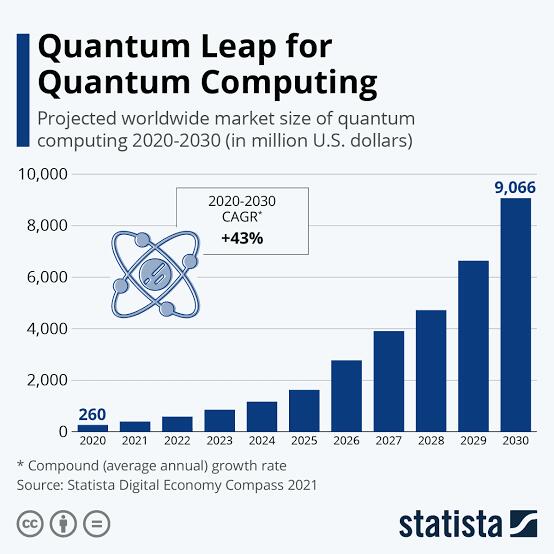 The Implications for Cybersecurity
The rise of quantum computing has significant implications for cybersecurity. Quantum computers can potentially break many of the encryption algorithms currently in use, which could compromise the security of online transactions and communication. This means that organizations and individuals will need to adopt new, quantum-resistant encryption algorithms to protect their data.
The Implications for Cybersecurity
The rise of quantum computing has significant implications for cybersecurity. Quantum computers can potentially break many of the encryption algorithms currently in use, which could compromise the security of online transactions and communication. This means that organizations and individuals will need to adopt new, quantum-resistant encryption algorithms to protect their data.
 The Impact on Data Protection
The rise of quantum computing also has significant implications for data protection. Quantum computers can potentially access and manipulate large amounts of data, which could compromise the privacy and security of individuals and organizations. This means that organizations and individuals will need to adopt new, quantum-resistant data protection measures to protect their data.
The Impact on Data Protection
The rise of quantum computing also has significant implications for data protection. Quantum computers can potentially access and manipulate large amounts of data, which could compromise the privacy and security of individuals and organizations. This means that organizations and individuals will need to adopt new, quantum-resistant data protection measures to protect their data.
 Preparing for a Quantum Future
To prepare for a future where quantum computers are a reality, organizations and individuals can take several steps:
1. Stay informed: Stay up-to-date with the latest developments in quantum computing and its implications for cybersecurity and data protection.
2. Adopt quantum-resistant encryption: Adopt new, quantum-resistant encryption algorithms to protect data from potential quantum computer attacks.
3. Implement quantum-resistant data protection measures: Implement new, quantum-resistant data protection measures to protect data from potential quantum computer attacks.
Preparing for a Quantum Future
To prepare for a future where quantum computers are a reality, organizations and individuals can take several steps:
1. Stay informed: Stay up-to-date with the latest developments in quantum computing and its implications for cybersecurity and data protection.
2. Adopt quantum-resistant encryption: Adopt new, quantum-resistant encryption algorithms to protect data from potential quantum computer attacks.
3. Implement quantum-resistant data protection measures: Implement new, quantum-resistant data protection measures to protect data from potential quantum computer attacks.Conclusion The rise of quantum computing has significant implications for cybersecurity and data protection. As quantum computers become more powerful and widely available, organizations and individuals will need to adopt new, quantum-resistant encryption algorithms and data protection measures to protect their data. By understanding the implications of quantum computing, we can take steps to prepare for a future where quantum computers are a reality.
Statistics: - The global quantum computing market is projected to reach $65 billion by 2025. (Source: MarketsandMarkets) - Quantum computers can potentially break many of the encryption algorithms currently in use, including RSA and elliptic curve cryptography. (Source: National Institute of Standards and Technology) - The use of quantum computers could compromise the security of online transactions and communication, potentially leading to significant financial losses. (Source: Ponemon Institute)
Sources: - “Quantum Computing Market” by Application, Industry, and Geography - Global Forecast to 2025" by MarketsandMarkets - "Post-Quantum Cryptography" by National Institute of Standards and Technology - "2019 Global Cybersecurity Survey" by Ponemon Institute
-
 @ ccc8ee23:9f3d9783
2024-12-19 12:46:00
@ ccc8ee23:9f3d9783
2024-12-19 12:46:00Chef's notes
Salmon Mentai Rice. Create your own layers of fluffy, seasoned rice are topped with tender, pan-seared chicken or salmon and a creamy, spicy mentai sauce made with spicy Japanese mayo .
Torched to golden perfection, it’s finished with nori and tobiko for a burst of texture and flavor. A simple tasty Japanese fusion delight that’s perfect🤩
Subtitude of Tobiko, white sesame seeds as economical option will add a nutty flavor and subtle crunch to the dish for texture and visual appeal.
Details
- ⏲️ Prep time: 10 min
- 🍳 Cook time: 30 min
- 🍽️ Servings: 2
Ingredients
- Steamed Rice 400 grams
- Rice vinegar 1 tbsp
- Sugar 1 tsp
- chicken breast / thighs 250 grams
- soy sauce 1 tbsp
- oyster sauce 1 tbsp
- sesame oil 1 tsp
- garlic powder 1 tsp
- cooking oil 1 tbsp
- mayonnaise (e.g., Kewpie) 4 tbsp
- sriracha or any chili sauce 1 tbsp
- tobiko if any or white sesame as optional, for texture, 2 tsp only
Directions
- Prepared the Rice: mixed in bowl 2 cups steam rice, 1 tbsp rice vinegar, 1 tsp sugar and 1/2 tsp salt. Set a side.
- Cook the Chicken: 1. Marinate the chicken pieces with 1 tsp soy sauce, 1 tsp oyster sauce, 1 tsp sesame oil, 1 tsp garlic powder for 15–20 minutes. 2. Heat cooking oil in a pan over medium heat and stir-fry the chicken until fully cooked and slightly caramelized. Remove from heat.
- Make the Mentai Sauce 1. In a small bowl, combine 4 tbsp mayonnaise, 1 tbsp chili sauce, and 1 tsp sesame oil. Add tobiko if desired for texture. Mix well.
- Assemble the Mentai Rice 1. In a heatproof bowl or tray, layer the seasoned rice as the base. 2. Add a layer of cooked chicken on top of the rice. 3. Spread the mentai sauce evenly over the chicken layer.
- Grill or Broil: Use a kitchen torch or place the dish under a broiler for 2–3 minutes until the sauce is slightly charred and bubbly.
- Garnish with white sesame or nori strips, or extra tobiko.
-
 @ 826e9f89:ffc5c759
2024-06-28 21:46:01
@ 826e9f89:ffc5c759
2024-06-28 21:46:01_Prologue: this is a prose adaptation of a talk I gave to a private audience in Dubai and then tweaked slightly for a small conference in Sofia. I'm increasingly thinking it deserves a more general audience, and may be better suited to text anyway. This is probably not its final form, as the desired audience is tradfi capital allocators, hence a PDF is likely on the cards in the near future. For the time being, consider this a first draft, practising what it might look like as prose, and soliciting feedback from the good people of Nostr. Enjoy! _
The title of this essay means absolutely nothing. There is no such thing as “Web π” because there is no such thing as “Web 3”. It’s bullshit. It’s a scam.
Unfortunately, it has turned out to be extremely powerful bullshit and an extremely profitable scam, and so my goal in writing this essay is to give the reader the tools to navigate all of this and come out the other side without having been scammed or bullshat. In the spirit of not scamming and not bullshitting, I should be clear upfront about the intended readership of this essay, who I am to write it, and who it’s really about.
Who Are You?
I assume the reader is not a shadowy super-coder, but rather is a financial professional. This essay isn’t really for Bitcoiners, although if any read it, I hope they still find it interesting. Who I am really writing for are people coming to the space for the first time. Hopefully in your mind you are coming to the _Bitcoin _space, but if you think you are coming to the “crypto” space then this may be even more useful.
Who Am I?
I am the founder of a company that makes me not only highly biased but also flagrantly self-interested in the content I am promoting. I run a firm that invests in the Bitcoin ecosystem through a variety of different vehicles. I am not going to mislead you in the slightest in that my primary motivation is for you to allocate capital to us rather than to people I would call scammers and bullshitters. You should listen to them too and make up your own mind, or else what’s the point, really? How do you know I’m not scamming or bullshitting you? Exactly. Don’t trust. Verify.
In any case, that’s all assuming you want to “allocate capital” at all rather than just buy Bitcoin without a management fee. I’d like to think the primary difference is that I will be honest about that, and I’ll encourage you to understand as much as you can about what is going on and what you are doing (and if you are at all unsure, I would suggest you aren’t ready and you should just buy Bitcoin and learn) rather than bamboozle you with complete nonsense like “Web 3”.
Who Is This About?
It’s not at all about people working in crypto. Bitcoiners amongst the readership may be mildly irritated by me going on to give about as charitable an explanation of the role of these people as they have probably ever heard from somebody like me. This is really about financiers. It’s about the people who have used the mostly unrewarded efforts of developers, academics, entrepreneurs, and so on to siphon money from you to themselves, leaving a trail of useless tech and defrauded retail investors in their wake – and who will continue to do so if you continue to empower them.
Why This Essay?
We are at an interesting point in the development of the entirety of the “crypto” industry and I strongly suggest that people like you are going to be pitched all kinds of scams and bullshit in the coming months and years. If you have a little more background on what these people are really talking about, you will hopefully be able to avoid it.
My plan to help with that is presenting a short version and a long version of what blockchains are and are for, how they have historically been deployed in service of scams and bullshit, a high-level theory explaining the narrative evolution behind this sorry history, and a prediction for the near-term future of such shenanigans.
What is a Blockchain For?
A Blockchain is for sound, censorship-resistant, peer-to-peer digital money. It is not for anything else. If a blockchain is functional as money, it may be possible to also _use it _for other things. Some people find that interesting, some people find it infuriating, but don’t let that subtlety confuse you. It is not _for _arbitrary computation and storage or “decentralizing the internet” or running illegal securities rackets.

It is for money, plain and simple.
How does it achieve that? Proof of work and the difficulty adjustment. These are the innovations from which every other desirable property or feature flows. Proof of work enables censorship resistance. If somebody is trying to sell you on “proof of stake”: bullshit. The difficulty adjustment enables precise, predetermined, and _fair _issuance. If somebody is trying to sell you on a token they issue for free and without restriction: scam.
The problem Bitcoin solves is both economic and technical and the solution has material technical and economic merit. And it’s for this very specific and irreplicable reason the Bitcoin token has value. If this all sounds extreme to you, then I would suggest that your understanding of the topic is _extremely _misguided, that you are going to be _extremely bullshat and extremely scammed, _and you need to read this essay. That’s the short version.
The Long Version
I am sensitive to how extreme this all sounds. After all, hundreds of billions of dollars have been pumped into crypto, not Bitcoin – a huge amount of it is widely used, and many capable, honest, and brilliant people work in the industry. The reader will recall just above I said those people are not the target of my criticism. I’m not claiming they are all scammers and bullshitters. Sadly, I think it’s more likely they have been scammed and bullshat to some degree also.
I think I have some credibility in pointing this out because, as a VC in the Bitcoin space, I have increasingly seen founders telling me this themselves: that they originally bought into the hype in crypto and ended up wasting an enormous amount of time realizing their idea made no technical or economic sense in that context, so then they came to Bitcoin instead. You hear this one time and it’s an anecdote, but you hear it as many times as I have and it feels more like a representative sample.
What I want to cover next is as charitable a summary of the state of ex-Bitcoin crypto as I possibly can: my contention is that crypto has evolved into 4 rough categories: stablecoins, cryptography R&D, gambling, and scams. And these aren’t exclusive, to be clear; there is a lot of overlap, and, in fact, the overlap is arguably the key.
Scams
Scams are tokens, plain and simple. If somebody is trying to profit from the speculative price action of a token they have issued, they are scamming somebody. Maybe they are scamming you, maybe they are scamming retail investors, maybe they are scamming customers or suppliers – if such parties even exist in their cargo cult “business model”. There’s a scam in there somewhere.
However, it is rarely _just _a scam. There will almost always be components of stablecoins, R&D or gambling too. Hence these are worth really grappling with, taking seriously, giving credit to the extent it is due, but also analyzing critically.
My rough and high-level assessment of this breakdown of crypto is as follows, and I’ll explain what I mean by this below: stablecoins have economic merit but dubious technical merit; R&D has technical merit but no economic merit; and gambling sort of has merit but it depends how you interpret it. Obviously, scams have neither.

Stablecoins
By “sort of technical merit” I mean that stablecoins have central issuers. You can issue them as tokens on a blockchain but there’s not really much of a point. The issuer could just run a database connected to the internet with some straightforward signature schemes for transfers and it would make minimal operational difference. In fact, it would be cheaper and faster. _In fact, _you may as well run a Chaumian eCash mint (a decades-old innovation recently resurrected firmly within the _Bitcoin _space) such that your cheaper-and-faster-than-a-blockchain database also grants users transience and privacy rather than the public permanence of a blockchain.
The fact Tron is the most heavily used for stablecoins, in terms of settling the most value, is a testament to this point: it is barely even pretending not to be a database. This works as regulatory arbitrage given regulators think this is “innovation” because they are stupid.
That said, it is worth giving some credit here given the abject awfulness of fiat banking and payment rails with which stablecoins arguably most directly compete. Stablecoins are significantly more permissionless in their transfer than any fiat bank liability. And to attest to what seems like their most significant use case, they are permissionless in their _usership _in that only an internet connection and the right software is required rather than various discriminatory jurisdictional and compliance criteria.
However, what “sort of technical merit” ultimately boils down to, especially in comparison to Bitcoin, is: highly censorable in their exogenous links and, therefore, their value. The assets supposedly backing stablecoins are (by definition) still within the fiat system, even if this novel transfer mechanism of the rights to withdraw them is not. There is frankly a bit of theatre involved in the so-called “decentralization” of stablecoins given shutting down the central issuer is all that is required to make the permissionlessly tradeable decentralized tokens go to zero and be technically unimpeded but functionally useless. The technical innovation of Bitcoin, in contrast, is easily understood in one sense as it being totally indifferent to this kind of attack.
On the other hand, by “economic merit” I mean that they are extremely widely used and valued as a means of providing dollar shadow banking and often superior payment rails. Those in crypto often love pointing to this and many Bitcoiners tie themselves in knots trying to explain it away, whereas I see it as essentially unrelated to Bitcoin. Clearly there is a superficial connection, but you could create any superficial connection by “tokenizing” things for no particularly good technical _reason. I think it’s a different industry entirely. It’s more like a subindustry within _fintech – part banking, part payments – that for the time being relies on bamboozling regulators with all the nonsense I’m drawing attention to.
And good for them, frankly. If fiat banking isn’t going to be backed by real money anyway, then it _at least _ought to be permissionless. It should really be Chaumian eCash if it isn’t just Bitcoin, and it is regulation alone that makes it so awful in the first place. Making money usable and not a tool of dystopian control is, at this point, a political problem, not a technical one. Stablecoins are frankly a step in the right direction, especially insofar as they acclimatize users to digital assets. But I would still caution that they arguably don’t have sufficient technical merit to withstand what feels like an inevitable political attack …
Cryptography R&D
“Technical merit” for R&D is more or less self-explanatory, but the context is worth appreciating. It’s only really in crypto and mostly in Ethereum more specifically that people can permissionlessly experiment with arbitrarily complex cryptographic schemes that operate on real, enormous value. There are a lot of people who understandably find this attractive given their projects are essentially academic and trying out their ideas in the wild is more interesting, arguably more worthwhile, and certainly more fun than putting research essays on ArXiv or submitting them to a journal.
But … the value being manipulated is at best stablecoins and at worst baseless hype. If it isn’t a stablecoin then it probably exists in the first place because of either gambling or scams – and even there the line is very blurry.
Gambling
Gambling is an interesting lens to adopt on all this because it’s literally a trillion-dollar industry. And it’s real. It’s consensual; it’s not criminal; it’s legitimate economic activity that generates enormous profits for those who facilitate it well.
So, gambling has economic merit in that sense. But it’s tricky in this context how to characterize it because you could also argue it’s deeply dishonest gambling in that the gamblers don’t realize they are playing a negative sum game against the house. They think they are doing something akin to speculating on securities, which may be just as stupid depending on how it’s done, but at least has real economic utility and contributes to capital formation.
The difference here is that what is being speculated on _has no economic merit. _So, if that’s your gauge of merit, then here there is none. And it’s a very blurry line between this and an outright scam. Maybe the people involved _think _of what they are doing as amazing R&D, and maybe it’s inadvertently just a scam; maybe they know it’s all nonsense, but they think they can profit within the negative sum game because there are greater fools. In any case, I think gambling is a very helpful characterization of a lot of the behavior of the users and the real economic function of the industry.
There’s an interesting social component to all this because crypto people will often get mad at Bitcoiners because Bitcoiners tend not to care about either stablecoins or crypto R&D: they’ll say, why don’t you like stablecoins, they have clear economic merit? And the answer is they have dubious technical merit. Or, why don’t you like our next-gen Zero Knowledge scaling protocol, it has clear technical merit? And the answer is it has no economic merit.
If you’re happy with one but not the other, it’s easy to think of Bitcoiners as being closed-minded or dogmatic or whatever, but, ultimately, I think it’s just about discipline. What’s the point in being excited by something that half works, and that you know why will never fully work? So to be frank, a lot of this may be well-intentioned, but it’s kinda’ bullshit. It very probably ultimately rests on gambling and not at all whatever its stated purpose is … or it’s just a scam.
How Did We Get Here?
The following is by no means exhaustive and the framing is deliberately a little tongue-in-cheek. As well as being accurate enough (if unavoidably biased), my goal here is primarily to set up my prediction for what is coming next.
2015 reality: Ethereum launches narrative: “the world computer”
In 2015, Ethereum launched. The narrative here was that we are building “the world computer” and we can now have decentralized uncensorable computation. Never mind that anybody with a laptop has an uncensorable and decentralized computing device. And keep in mind this question of, “_what data might it ever be relevant to compute over in this manner (whatever that means in the first place)?” _The answer will become clearer and clearer …
2016-17 reality: ICO bubble narrative: “Web 3” / “DApps”
Regardless, at the end of 2015 we get the proposal and adoption of ERC20: a standard for issuing fungible tokens within Ethereum contracts, which is why in 2016 _but especially in 2017 _we get the ICO bubble. The narrative changes. Now we are concerned with “Web 2” companies being huge, powerful, and centralized. What if, instead, users could cooperatively own the application, control their own data, and participate in the economic upside that their usage is creating?
2018-19 reality: crypto winter narrative: “mistakes were made”
In 2018 this all falls apart, so don’t worry about it, moving on …
2020-21 reality: defi summer narrative: “decentralized finance”
By 2020 the narrative was different once again. It is more or less realized by this point that utility tokens make no technical or economic sense. You can’t introduce artificial scarcity in capital goods where there should be abundance and deflation and expect anybody to care, never mind to value your concoction. On the other hand, “securities” ought to be scarce and in some sense ought to function as tradeable ledger entries. Maybe they could be tokenized and computed on in a censorship-resistant and decentralized manner?
So, we get a boom in “defi” which, for what it’s worth, fellow Axiom co-founder Anders Larson and I predicted in our essay Only The Strong Survive, in September 2021, would be a complete disaster because, amongst a myriad of other illiterate insanities, there was approximately zero grounding of these securities in productive capital. The ecosystem was entirely self-referential – grounded _not even _in the questionable economic merit of stablecoins but firmly in gambling and scams; in leverage, rehypothecation, and securitization of precisely nothing whatsoever productive.
2022 reality: shitcoinpocalypse narrative: “mistakes were made”
And we were absolutely right because in 2022 everything collapsed. First Terra/Luna imploded – a “defi” project which essentially presented to the world the argument that a fractional reserve bank issuing fiduciary media can literally never go bankrupt because it can always cover a deposit shortfall by issuing more equity. While briefly flirting with a capitalization of around fifty f***ing billion dollars, and endorsed and fawned over by all manner of illiterate charlatans with gigantic and unsuspecting audiences, this argument was eventually rejected by the market as utterly imbecilic, as analyzed by myself and Nic Carter in All Falls Down.
This triggered a credit contagion that soon after took down 3 Arrows Capital, Celsius, Voyager, BlockFi, and others. FTX limped along by what we now understand to be something like defrauding their way out of debt, but eventually also collapsed later that year. If _Only The Strong Survive _was a pre-mortem of all of this, then the reader may want to read Green Eggs And Ham, also by myself and Anders Larson, as a kind of post-mortem.
2023-today reality: Bitcoin multisigs narrative: “Bitcoin renaissance”
And now a lot of this stuff is moving to Bitcoin. It is outside the scope of this essay to explain this in much detail but there have been a handful of developments in Bitcoin recently which, regardless of their intended purpose, seem to have as a collective side effect that a lot of these same shenanigans can now be implemented (or can _pretend _to be implemented) in a more Bitcoin-native context.
So, the new narrative is something like:
“these things didn’t work, not because they are terrible ideas that collapse to moon math wrappers around gambling and scams under any remotely critical analysis, but rather because they weren’t on Bitcoin. But also, since it has only recently become possible to (at least pretend to) implement them on Bitcoin, they are now worthwhile. We have wandered in the wilderness but learned our lessons and found the promised land.”

Technical and Economic Merit
Let’s consider all this through the lens of technical and economic merit once again. Or rather, the alleged merit given the stated goal. Ignore for now whether there is any merit:
2015 technical goal: new computing paradigm economic goal: x% of GDP?
The original idea of “crypto” allegedly has the merit of the next revolution in computing. Goodness knows how big that market is; probably a decent chunk of global GDP – if it meant anything, which it doesn’t.
2016-17 technical goal: disrupting company formation economic goal: y% of S&P?
ICOs then become a little bit more specific. Now they are merely disrupting how we organize companies. What’s that worth? Some portion of the value of the companies that can now be decentralized and tokenized I guess? Who knows …
2018-19 nothing to see here
Nothing happened then, don’t worry about it.
2020-21 technical goal: decentralize finance economic goal: z% of NYSE, CME, ISDA?
Defi becomes more specific again. Now we are merely tokenizing financial contracts, expanding access, removing middlemen, and so on. So that should probably be worth some percentage of capital markets activity?
2022 nothing to see here
Oops, never mind …
2023-today technical goal: now it’s on Bitcoin! economic goal: i% of … Bitcoin?
… and now it’s on Bitcoin apparently.
In Hindsight ...
I think the most amusing analysis of all this is as follows: it starts off completely insane, it gets more and more restrained each time – you could cheekily argue it starts to make more and more sense – but it also gets closer to Bitcoin every time. It’s clearly narrowing in on just: Bitcoin.
This is people realizing, painfully, over decades, what blockchains are for! They are not for “decentralizing everything” They are for censorship-resistant, sound, peer-to-peer digital money.

And I think this is _also _why we get the current state of crypto from earlier in the essay. As it starts to make more and more sense (by getting closer and closer to Bitcoin) you have realizations like the following: digital gift vouchers for artificially scarce and extremely expensive computation aren’t money, so we need “real money” in here for it to have economic merit, so you get stablecoins. Also, well we have a rich programming environment that seems technically interesting but also the severe technical handicap of being unable to do even a billionth of a billionth of a billionth of all the computations in the world, so you get crypto R&D. These emerge as a kind of patch, and they have _some _merit in isolation, whereas the long-term trajectory is actually just to converge on Bitcoin.
It’s an open and fascinating question if there are any learnings from these that can still be transplanted to Bitcoin. For stablecoins, this strikes me as less clear, given the dubious technical merit is introduced by using a blockchain at all, not just a blockchain other than Bitcoin. However, efforts to create Bitcoin balances (tokenized or otherwise) that are stable relative to some external price are to be applauded, if still heavily scrutinized for what technical merit they _really _have.
It seems far more likely that crypto R&D will prove useful in a Bitcoin context to some or other degree, and in this case the economic merit is in fact solved by moving to Bitcoin, provided the necessary technical merit can be mimicked. At the time of writing, this is a source of both hope and dread: hope given the possibility of viable avenues of development (although still highly uncertain); dread given how early steps in this direction are already being misrepresented in the pursuit of bullshit and scams. I will return to both shortly.
Narrative Evolution
Back to the table just above, I want to make three quick observations that tie together my entire argument and get us to the end of the essay:

Firstly, the bubbles always follow the price of Bitcoin. Hopefully I don’t need to include a price chart for the reader to grasp this immediately.
Secondly, it’s important that the narrative always changes. Absolutely ungodly amounts of money were raised for this crap following the_ Bitcoin bull runs of 2017 and 2021. The people doing this couldn’t point to the previous absolute disaster, so they had to spin something along the lines of: “_we learned our lessons and we’ve refined the use case.” This should sound familiar from just above.
Thirdly, however, regardless of whatever refinement they’ve come up with, the consequence of the new “narrative” is always, “buy my token”.
Always.
It doesn’t matter what buzzword salad is in the middle. It’s always “Bitcoin is cool, xyz, fughayzi fughahzi, buy my token.”
This is why I am very much tempted to not care so much about developers, academics, entrepreneurs, and so on, and in fact for my null hypothesis to be that they are more likely to have been victims than perpetrators. I don’t think they even end up in a position to contribute without the key group whom I do blame. When you put all these pieces together, what I think falls out of this analysis is as follows:
The entire cycle of shitcoinery can be traced to unscrupulous financiers convincing capital allocators who don’t know any better, in a bull market that, yes, Bitcoin is cool, but what they are doing is related, cooler, and that they deserve a fee.
Let us label this the Capital Cycle Theory of Shitcoinery. I think that everything else about which one might want to complain is downstream of this core realization.
Avoiding It
Given everything I’ve covered this is simple and this is pretty much the end of the essay.
You need to be aware of why this is happening now. If it hasn’t happened to you already (intended readership in the capital allocation business, that is) I guarantee it’s about to: with ETFs and the halving just past, we seem to be starting a Bitcoin bull run, these people have already raised ridiculous amounts of money on scams and bullshit that have mostly imploded. They may have lost a lot of money, or they may even have dumped on retail and got an excellent “return”. But in any case, they need a new narrative.
It's _possible _they have a viable narrative around stablecoins, R&D, both, and that they are as wary of scams as I have suggested here that they should be. I don’t want to insult anybody who merely has a different investment thesis to me if they are otherwise reasonable in their outlook and honest in their dealings.
However, if they are only now realizing how pointless and disingenuous every preceding crypto narrative has been after 7 years and hundreds of billions of dollars – or if they still don’t realize it at all; if their track record shows they were deeply involved, handsomely rewarded, and yet created nothing of lasting value; if they say things like “the builders are coming back to Bitcoin”: be very, very suspicious. Be on the lookout for tokens, which is to say, be on the lookout for scams.
What is especially frustrating is that the technical spin of the "layer twos" that are all the rage at the time of writing, that "the builders are coming back to Bitcoin" to build, and that you, the capital-allocating reader, will almost certainly be pitched, is in and of itself pretty reasonable. They just don't require tokens and they don't require gambling to support the token prices. What they do require is _sound adherence to Bitcoin's technical and economic merit. _At the very least, they require honest communication about the design trade-offs so far and planned for, and what, if any, economic and technical merit is left over after these trade-offs have been made.
Narrative aside, the _reality _of 99% of these projects is that they are private execution environments tied to multisigs custodying user deposits. Which is to say, on the one hand, that they are cargo culting "crypto R&D" from Ethereum that isn't technically possible in Bitcoin in order to feign technical merit, and on the other, that _they aren't layer twos at all. _Once again, they may as well be Chaumian eCash mints, except for the fact that this would make the intended token scam all but impossible to pull off.
Casey Rodarmor, creator of the Ordinals protocol, recently joked on the Hell Money _podcast he co-hosts, responding to the idea that "_everybody is building an L2 now":
"It's the same sad sack playbook as on Ethereum being recapitulated on Bitcoin. That's how you get a VC check on Ethereum. They are all glorified multisigs, so they are like, "hey let's port our glorified multisig to Bitcoin and get a VC check." I was talking to a friend of mine who is working on an interesting project, an open-source analyzer that does transaction clustering, and I was like, "maybe you could do this in this way and raise some VC money," and he said, "yeah, okay, but what's the point in raising VC money?" And I said, "no, no, no, this is the end! This is the goal! You raise VC money and then you cut yourself checks from that VC money until it runs out and then you raise more at a 10x valuation. This is the new economy, guys!"
The 1% that are legitimately trying to bring the learnings from crypto R&D to Bitcoin in a technically and economically sound manner will hopefully win in the long run (and even this is somewhat speculative at the time of writing) but will likely get little to no attention amidst this bull market flurry of scams and bullshit.
Axiom will do its best to source and invest in these companies (we already have!) but we are resigned to it being a much more difficult sell to capital allocators in light of the Capital Cycle Theory of Shitcoinery. To be brutally honest, this entire essay can fairly be considered cope on my part in light of having lost this battle in the past and facing up to the very real prospect of losing it in the near future too. Oh well, at least I tried.
Wrapping Up
The essence of the Capital Cycle Theory of Shitcoinery is that the problems I’ve described ultimately come from bamboozling people just like you with technical sounding nonsense like “Web 3” so you think it’s all a lot more complicated than it really is. Just buy Bitcoin. That’s certainly the first thing you should do anyway, and it might be the only thing you ever need to do.
If you really, really want to take the extra risk of investing in the Bitcoin ecosystem, the team at Axiom would be happy to speak with you. But we are never going to talk you out of buying Bitcoin. There is no world in which Bitcoin does poorly and we do well, or in which we promise something “better than Bitcoin,” and there’s no point in engaging with us at all if you don’t already believe most of this.
If that’s of interest to you, we’d love to talk. If not, just buy Bitcoin. In any case: fair warning, we are heading into a Bitcoin bull market and the scams and the bullshit are coming. Good luck avoiding them.
Allen Farrington, June 2024

-
 @ f4db5270:3c74e0d0
2024-12-20 11:13:58
@ f4db5270:3c74e0d0
2024-12-20 11:13:58Hi Art lover! 🎨🫂💜 You may not know it yet but all of the following paintings are available in #Bitcoin on my website: https://isolabell.art/#shop
For info and prices write to me in DM and we will find a good deal! 🤝
And remember, FREE SHIPPING until the end of the year. 🤩
 THE BLUE HOUR
40x50cm, Oil on canvas
Completed December 14, 2024
THE BLUE HOUR
40x50cm, Oil on canvas
Completed December 14, 2024
 LIKE A FRAGMENT OF ETERNITY
50x40cm, Oil on canvas
Completed December 01, 2024
LIKE A FRAGMENT OF ETERNITY
50x40cm, Oil on canvas
Completed December 01, 2024
 WHERE WINTER WHISPERS
50x40cm, Oil on canvas
Completed November 07, 2024
WHERE WINTER WHISPERS
50x40cm, Oil on canvas
Completed November 07, 2024
 L'ATTESA DI UN MOMENTO
40x40cm, Oil on canvas
Completed October 29, 2024
L'ATTESA DI UN MOMENTO
40x40cm, Oil on canvas
Completed October 29, 2024
 LE COSE CHE PENSANO
40x50cm, Oil on paper
Completed October 05, 2024
LE COSE CHE PENSANO
40x50cm, Oil on paper
Completed October 05, 2024
 TWILIGHT'S RIVER
50x40cm, Oil on canvas
Completed September 17, 2024
TWILIGHT'S RIVER
50x40cm, Oil on canvas
Completed September 17, 2024
 GOLD ON THE OCEAN
40x50cm, Oil on paper
Completed September 08, 2024
GOLD ON THE OCEAN
40x50cm, Oil on paper
Completed September 08, 2024
 SUSSURRI DI CIELO E MARE
50x40cm, Oil on paper
Completed September 05, 2024
SUSSURRI DI CIELO E MARE
50x40cm, Oil on paper
Completed September 05, 2024
 THE END OF A WONDERFUL WEEKEND
40x30cm, Oil on board
Completed August 12, 2024
THE END OF A WONDERFUL WEEKEND
40x30cm, Oil on board
Completed August 12, 2024
 FIAMME NEL CIELO
60x35cm, Oil on board
Completed July 28, 2024
FIAMME NEL CIELO
60x35cm, Oil on board
Completed July 28, 2024
 INIZIO D'ESTATE
50x40cm, Oil on cradled wood panel
Completed July 13, 2024
INIZIO D'ESTATE
50x40cm, Oil on cradled wood panel
Completed July 13, 2024
 OMBRE DELLA SERA
50x40cm, Oil on cradled wood panel
Completed June 16, 2024
OMBRE DELLA SERA
50x40cm, Oil on cradled wood panel
Completed June 16, 2024
 NEW ZEALAND SUNSET
80x60cm, Oil on canvas board
Completed May 28, 2024
NEW ZEALAND SUNSET
80x60cm, Oil on canvas board
Completed May 28, 2024
 VENICE
50x40cm, Oil on board
Completed May 4, 2024
VENICE
50x40cm, Oil on board
Completed May 4, 2024
 CORNWALL
50x40cm, Oil on board
Completed April 26, 2024
CORNWALL
50x40cm, Oil on board
Completed April 26, 2024
 DOCKS ON SUNSET
40x19,5cm, Oil on board
Completed March 14, 2024
DOCKS ON SUNSET
40x19,5cm, Oil on board
Completed March 14, 2024
 SOLITUDE
30x30cm, Oil on cradled wood panel
Completed March 2, 2024
SOLITUDE
30x30cm, Oil on cradled wood panel
Completed March 2, 2024
 LULLING WAVES
40x30cm, Oil on cradled wood panel
Completed January 14, 2024
LULLING WAVES
40x30cm, Oil on cradled wood panel
Completed January 14, 2024
 MULATTIERA IN AUTUNNO
30x30cm, Oil on cradled wood panel
MULATTIERA IN AUTUNNO
30x30cm, Oil on cradled wood panel
 TRAMONTO A KOS
40x40cm, oil on board canvas
TRAMONTO A KOS
40x40cm, oil on board canvas
 HIDDEN SMILE
40x40cm, oil on board
HIDDEN SMILE
40x40cm, oil on board
 INIZIO D'AUTUNNO
40x40cm, oil on canvas
INIZIO D'AUTUNNO
40x40cm, oil on canvas
 BOE NEL LAGO
30x30cm, oil on canvas board
BOE NEL LAGO
30x30cm, oil on canvas board
 BARCHE A RIPOSO
40x40cm, oil on canvas board
BARCHE A RIPOSO
40x40cm, oil on canvas board
 IL RISVEGLIO
30x40cm, oil on canvas board
IL RISVEGLIO
30x40cm, oil on canvas board
 LA QUIETE PRIMA DELLA TEMPESTA
30x40cm, oil on canvas board
LA QUIETE PRIMA DELLA TEMPESTA
30x40cm, oil on canvas board
 LAMPIONE SUL LAGO
30x30cm, oil on canvas board
LAMPIONE SUL LAGO
30x30cm, oil on canvas board
 DUE NELLA NEVE
60x25cm, oil on board
DUE NELLA NEVE
60x25cm, oil on board
 UNA CAREZZA
30x30cm, oil on canvas board
UNA CAREZZA
30x30cm, oil on canvas board
 REBEL WAVES
44x32cm, oil on canvas board
REBEL WAVES
44x32cm, oil on canvas board
 THE SCREAMING WAVE
40x30cm, oil on canvas board
THE SCREAMING WAVE
40x30cm, oil on canvas board
 "LA DONZELLETTA VIEN DALLA CAMPAGNA..."
30x40cm, oil on canvas board
"LA DONZELLETTA VIEN DALLA CAMPAGNA..."
30x40cm, oil on canvas board
 LIGHTHOUSE ON WHITE CLIFF
30x40cm, oil on canvas board
LIGHTHOUSE ON WHITE CLIFF
30x40cm, oil on canvas board
-
 @ 6ad3e2a3:c90b7740
2024-12-20 09:35:27
@ 6ad3e2a3:c90b7740
2024-12-20 09:35:27This event has been deleted; your client is ignoring the delete request.
-
 @ 4523be58:ba1facd0
2024-05-28 11:05:17
@ 4523be58:ba1facd0
2024-05-28 11:05:17NIP-116
Event paths
Description
Event kind
30079denotes an event defined by its event path rather than its event kind.The event directory path is included in the event path, specified in the event's
dtag. For example, an event path might beuser/profile/name, whereuser/profileis the directory path.Relays should parse the event directory from the event path
dtag and index the event by it. Relays should support "directory listing" of kind30079events using the#ffilter, such as{"#f": ["user/profile"]}.For backward compatibility, the event directory should also be saved in the event's
ftag (for "folder"), which is already indexed by some relay implementations, and can be queried using the#ffilter.Event content should be a JSON-encoded value. An empty object
{}signifies that the entry at the event path is itself a directory. For example, when savinguser/profile/name:Bob, you should also saveuser/profile:{}so the subdirectory can be listed underuser.In directory names, slashes should be escaped with a double slash.
Example
Event
json { "tags": [ ["d", "user/profile/name"], ["f", "user/profile"] ], "content": "\"Bob\"", "kind": 30079, ... }Query
json { "#f": ["user/profile"], "authors": ["[pubkey]"] }Motivation
To make Nostr an "everything app," we need a sustainable way to support new kinds of applications. Browsing Nostr data by human-readable nested directories and paths rather than obscure event kind numbers makes the data more manageable.
Numeric event kinds are not sustainable for the infinite number of potential applications. With numeric event kinds, developers need to find an unused number for each new application and announce it somewhere, which is cumbersome and not scalable.
Directories can also replace monolithic list events like follow lists or profile details. You can update a single directory entry such as
user/profile/nameorgroups/follows/[pubkey]without causing an overwrite of the whole profile or follow list when your client is out-of-sync with the most recent list version, as often happens on Nostr.Using
d-tagged replaceable events for reactions, such as{tags: [["d", "reactions/[eventId]"]], content: "\"👍\"", kind: 30079, ...}would make un-reacting trivial: just publish a new event with the samedtag and an empty content. Toggling a reaction on and off would not cause a flurry of new reaction & delete events that all need to be persisted.Implementations
- Relays that support tag-replaceable events and indexing by arbitrary tags (in this case
f) already support this feature. - IrisDB client side library: treelike data structure with subscribable nodes.
https://github.com/nostr-protocol/nips/pull/1266
- Relays that support tag-replaceable events and indexing by arbitrary tags (in this case
-
 @ ccc8ee23:9f3d9783
2024-12-19 05:55:09
@ ccc8ee23:9f3d9783
2024-12-19 05:55:09Chef's notes
Dare to taste the bold? One bite of Jengkol Balado and you’ll be hooked
Spicy Jengkol Balado - Betawi Style A traditional dish from Betawi (Jakarta), Jengkol Balado is nutty bold and aromatic delicacy made with jengkol beans. This version uses thinly sliced jengkol for a delightful texture.
Serve it with a plate of steamed fragrant white rice and a side of crunchy cucumber for a complete meal that satisfies on every level.
Details
- 🍳 Cook time: 40 min
- 🍽️ Servings: 2
Ingredients
- Jengkol 250 grams
- Chilli 100 grams
- Shallot 5 cloves
- Garlic 2 cloves
- Tomato 1 clove (small)
- Bay leaves 2
- Galangal 2cm. Bruished
- Veggie oil 20ml or 4 tsp
- Seasoning
Directions
- Prepare the Jengkol Wash the jengkol thoroughly and slice it thinly. Boil the slices in water with the bay leaves for 10–15 minutes to soften and reduce their strong odour. Drain and set aside.
- Make the Balado Paste. Blend chillies, shallots, garlic, candlenut and tomatoes into a slightly coarse paste using a blender
- Heat oil in a pan and sauté the balado paste until fragrant and the oil starts to separate. Add the galangal, bay leaves, salt, sugar, and seasoning. Stir well
- Add jengkol to the pan. Mix until jengkol are fully coated in the balado paste.
- If the mixture seems too dry, add a splash of water and let it simmer on low heat to allow the flavours to infuse.
- Taste the dish and adjust the seasoning with more salt or sugar if needed.
- Remove from heat and serve hot with steamed rice.
-
 @ ac8bb9b0:70278acc
2024-12-18 21:18:57
@ ac8bb9b0:70278acc
2024-12-18 21:18:57Details
- ⏲️ Prep time: 10
- 🍳 Cook time: 20
- 🍽️ Servings: 5
Ingredients
- 8 ounces uncooked linguine
- 1 pound chicken breast, cut into strips
- 1-2 tsp Cajun seasoning, or more to taste
- 1 tsp garlic powder
- 1 tbsp extra virgin olive oil
- 1 medium red bell pepper, thinly sliced
- 1 medium yellow bell pepper, thinly sliced
- 8 oz fresh mushrooms, sliced
- 1/2 red onion, sliced
- 3 cloves garlic, minced
- 2 tomatoes, diced
- 1 cup low sodium chicken broth
- 1/3 cup skim milk
- 1 tbsp flour
- 3 tbsp light cream cheese
- fresh cracked pepper
- 2 scallions, chopped
- kosher salt to taste
- avocado oil spray
Directions
- Prep all your vegetables.
- In a small blender make a slurry by combining milk, flour and cream cheese. Set aside.
- Season chicken generously with Cajun seasoning, garlic powder and salt.
- Prepare pasta in salted water according to package directions.
- Heat a large heavy nonstick skillet over medium-high heat; spray with oil and add half of the chicken.
- Sauté 5 to 6 minutes or until done, set aside on a plate and repeat with the remaining chicken. Set aside.
- Add olive oil to the skillet and reduce to medium; add bell peppers, onions, and garlic to skillet, sauté 3-4 minutes.
- Add mushrooms and tomatoes and sauté 3-4 more minutes or until vegetables are tender.
- Season with 1/4 tsp salt, garlic powder and fresh cracked pepper to taste.
- Reduce heat to medium-low; add chicken broth and pour in slurry stirring about 2 minutes.
- Return chicken to skillet; adjust salt and Cajun seasoning to taste, cook another minute or two until hot, then add linguine; toss well to coat.
- Top with chopped scallions and enjoy!
-
 @ b60c3e76:c9d0f46e
2024-05-15 10:08:47
@ b60c3e76:c9d0f46e
2024-05-15 10:08:47KRIS menjamin semua golongan masyarakat mendapatkan perlakuan sama dari rumah sakit, baik pelayanan medis maupun nonmedis.
Demi memberikan peningkatan kualitas layanan kesehatan kepada masyarakat, pemerintah baru saja mengeluarkan Peraturan Presiden (Perpres) nomor 59 tahun 2024 tentang Jaminan Kesehatan. Melalui perpres itu, Presiden Joko Widodo (Jokowi) telah menghapus perbedaan kelas layanan 1, 2, dan 3 dalam Badan Penyelenggara Jaminan Sosial atau BPJS Kesehatan.
Layanan berbasis kelas itu diganti dengan KRIS (Kelas Rawat Inap Standar). Berkaitan dengan lahirnya Perpres 59/2024 tentang Perubahan Ketiga atas Perpres 82/2018 tentang Jaminan Kesehatan, Presiden Joko Widodo telah memerintahkan seluruh rumah sakit yang bekerja sama dengan BPJS Kesehatan melaksanakannya.
Kebijakan baru itu mulai berlaku per 8 Mei 2024 dan paling lambat 30 Juni 2025. Dalam jangka waktu tersebut, rumah sakit dapat menyelenggarakan sebagian atau seluruh pelayanan rawat inap berdasarkan KRIS sesuai dengan kemampuan rumah sakit.
Lantas apa yang menjadi pembeda dari sisi layanan dengan layanan rawat inap sesuai Perpres 59/2024? Dahulu sistem layanan rawat BPJS Kesehatan dibagi berdasarkan kelas yang dibagi masing-masing kelas 1, 2, dan 3. Namun, melalui perpres, layanan kepada masyarakat tidak dibedakan lagi.
Pelayanan rawat inap yang diatur dalam perpres itu--dikenal dengan nama KRIS—menjadi sistem baru yang digunakan dalam pelayanan rawat inap BPJS Kesehatan di rumah sakit-rumah sakit. Dengan KRIS, semua golongan masyarakat akan mendapatkan perlakuan yang sama dari rumah sakit, baik dalam hal pelayanan medis maupun nonmedis.
Dengan lahirnya Perpres 59/2024, tarif iuran BPJS Kesehatan pun juga akan berubah. Hanya saja, dalam Perpres itu belum dicantumkan secara rinci ihwal besar iuran yang baru. Besaran iuran baru BPJS Kesehatan itu sesuai rencana baru ditetapkan pada 1 Juli 2025.
“Penetapan manfaat, tarif, dan iuran sebagaimana dimaksud ditetapkan paling lambat tanggal 1 Juli 2025,” tulis aturan tersebut, dikutip Senin (13/5/2024).
Itu artinya, iuran BPJS Kesehatan saat ini masih sama seperti sebelumnya, yakni sesuai dengan kelas yang dipilih. Namun perpres itu tetap berlaku sembari menanti lahirnya peraturan lanjutan dari perpres tersebut.
Kesiapan Rumah Sakit
Berkaitan dengan lahirnya kebijakan layanan kesehatan tanpa dibedakan kelas lagi, Kementerian Kesehatan (Kemenkes) menegaskan mayoritas rumah sakit di Indonesia siap untuk menjalankan layanan KRIS untuk pasien BPJS Kesehatan.
Kesiapan itu diungkapkan oleh Dirjen Pelayanan Kesehatan Kemenkes Azhar Jaya. “Survei kesiapan RS terkait KRIS sudah dilakukan pada 2.988 rumah sakit dan yang sudah siap menjawab isian 12 kriteria ada sebanyak 2.233 rumah sakit,” ujar Azhar.
Sebagai informasi, KRIS adalah pengganti layanan Kelas 1, 2, dan 3 BPJS Kesehatan yang bertujuan untuk memberikan layanan kesehatan secara merata tanpa melihat besaran iurannya.
Melalui KRIS, rumah sakit perlu menyiapkan sarana dan prasarana sesuai dengan 12 kriteria kelas rawat inap standar secara bertahap. Apa saja ke-12 kriteria KRIS itu?
Sesuai bunyi Pasal 46A Perpres 59/2024, disyaratkan kriteria fasilitas perawatan dan pelayanan rawat inap KRIS meliputi komponen bangunan yang digunakan tidak boleh memiliki tingkat porositas yang tinggi serta terdapat ventilasi udara dan kelengkapan tidur.
Demikian pula soal pencahayaan ruangan. Perpres itu juga mengatur pencahayaan ruangan buatan mengikuti kriteria standar 250 lux untuk penerangan dan 50 lux untuk pencahayaan tidur, temperature ruangan 20--26 derajat celcius.
Tidak hanya itu, layanan rawat inap berdasarkan perpres itu mensyaratkan fasilitas layanan yang membagi ruang rawat berdasarkan jenis kelamin pasien, anak atau dewasa, serta penyakit infeksi atau noninfeksi.
Selain itu, kriteria lainnya adalah keharusan bagi penyedia layanan untuk mempertimbangkan kepadatan ruang rawat dan kualitas tempat tidur, penyediaan tirai atau partisi antartempat tidur, kamar mandi dalam ruangan rawat inap yang memenuhi standar aksesibilitas, dan menyediakan outlet oksigen.
Selain itu, kelengkapan tempat tidur berupa adanya dua kotak kontak dan nurse call pada setiap tempat tidur dan adanya nakas per tempat tidur. Kepadatan ruang rawat inap maksimal empat tempat tidur dengan jarak antara tepi tempat tidur minimal 1,5 meter.
Tirai/partisi dengan rel dibenamkan menempel di plafon atau menggantung. Kamar mandi dalam ruang rawat inap serta kamar mandi sesuai dengan standar aksesibilitas dan outlet oksigen.
Azhar menjamin, Kemenkes akan menjalankan hal tersebut sesuai dengan tupoksi yang ada. “Tentu saja kami akan bekerja sama dengan BPJS Kesehatan dalam implementasi dan pengawasannya di lapangan,” ujar Azhar.
Berkaitan dengan perpres jaminan kesehatan itu, Direktur Utama BPJS Kesehatan Ghufron Mukti menilai, perpres tersebut berorientasi pada penyeragaman kelas rawat inap yang mengacu pada 12 kriteria. "Bahwa perawatan ada kelas rawat inap standar dengan 12 kriteria, untuk peserta BPJS, maka sebagaimana sumpah dokter tidak boleh dibedakan pemberian pelayan medis atas dasar suku, agama, status sosial atau beda iurannya," ujarnya.
Jika ada peserta ingin dirawat pada kelas yang lebih tinggi, kata Ghufron, maka diperbolehkan selama hal itu dipengaruhi situasi nonmedis. Hal itu disebutkan dalam Pasal 51 Perpres Jaminan Kesehatan diatur ketentuan naik kelas perawatan.
Menurut pasal tersebut, naik kelas perawatan dilakukan dengan cara mengikuti asuransi kesehatan tambahan atau membayar selisih antara biaya yang dijamin oleh BPJS Kesehatan dengan biaya yang harus dibayar akibat peningkatan pelayanan.
Selisih antara biaya yang dijamin oleh BPJS Kesehatan dengan biaya pelayanan dapat dibayar oleh peserta bersangkutan, pemberi kerja, atau asuransi kesehatan tambahan.
Ghufron Mukti juga mengimbau pengelola rumah sakit tidak mengurangi jumlah tempat tidur perawatan pasien dalam upaya memenuhi kriteria KRIS. "Pesan saya jangan dikurangi akses dengan mengurangi jumlah tempat tidur. Pertahankan jumlah tempat tidur dan penuhi persyaratannya dengan 12 kriteria tersebut," tegas Ghufron.
Penulis: Firman Hidranto Redaktur: Ratna Nuraini/Elvira Inda Sari Sumber: Indonesia.go.id
-
 @ ac8bb9b0:70278acc
2024-12-16 19:37:12
@ ac8bb9b0:70278acc
2024-12-16 19:37:12Details
- ⏲️ Prep time: 10
- 🍳 Cook time: 20
- 🍽️ Servings: 6
Ingredients
- 2 tablespoons extra virgin olive oil
- 1 1/2 pounds ground chicken
- 1 yellow onion, chopped
- 2 tablespoons taco seasoning
- salt and black pepper
- 2 1/2 cups salsa or enchilada sauce
- 1 chipotle chili in adobo, chopped
- 2 cups fresh corn
- 4 ounces cream cheese, at room temperature
- 1/4 cup plain greek yogurt
- 1 teaspoon chili powder
- 1 1/2 cups shredded Mexican cheese blend
- 2 cups tortilla chips
- avocado, cilantro, and green onions, for serving
Directions
- Preheat the oven to 400° F.
- In a large oven-safe skillet, combine the olive oil, chicken, onion, salt, and pepper. Set the skillet over high heat. Cook, breaking up the meat as it cooks, until browned all over, 5 minutes. Add the taco seasoning, cook another 2 minutes. Then add 1/2 cup water. Stir in the salsa/enchilada sauce and chipotle. Simmer 5 minutes. Remove from the heat and add in the cilantro.
- In a bowl, combine the corn, cream cheese, yogurt, chili powder, and salt. Stir in 1/2 cup cheese.
- Dollop 1/3 of the corn mix over the skillet. Add the tortilla chips on top, pressing them gently into the skillet. Add the remaining corn mix by spoonfuls on top of the chips (like nachos). Top with the remaining cheese. Bake for 15 minutes, until the cheese is melted.
- Serve topped as desired with avocado, cilantro, green onion, and cotija/feta cheese.
-
 @ a383f86d:cdb417d4
2024-12-20 05:02:32
@ a383f86d:cdb417d4
2024-12-20 05:02:32188BET là một nền tảng tiên phong, được thiết kế để mang lại trải nghiệm kỹ thuật số chất lượng cao cho người dùng. Với sự kết hợp giữa công nghệ hiện đại và thiết kế tinh tế, 188BET không chỉ đáp ứng nhu cầu của người dùng mà còn vượt qua mọi kỳ vọng. Nền tảng này tạo ra một môi trường năng động, nơi mọi người có thể tận hưởng các tính năng đa dạng và hiện đại, đồng thời luôn đặt sự hài lòng của khách hàng lên hàng đầu.
Giao diện của 188BET được thiết kế trực quan và thân thiện với người dùng, giúp việc truy cập và sử dụng trở nên dễ dàng hơn bao giờ hết. Từ lần đầu tiên sử dụng, người dùng có thể cảm nhận được sự tiện lợi và hiệu quả của các tính năng. Mỗi chi tiết trong thiết kế đều được tối ưu hóa để mang lại trải nghiệm mượt mà, phù hợp với mọi đối tượng. Điều này không chỉ giúp tăng tính tương tác mà còn tạo nên ấn tượng chuyên nghiệp cho nền tảng. https://188bet-vi.com
Bảo mật là một trong những yếu tố ưu tiên hàng đầu của 188BET. Với công nghệ mã hóa tiên tiến và các biện pháp bảo vệ nghiêm ngặt, nền tảng này đảm bảo an toàn tuyệt đối cho dữ liệu và thông tin của người dùng. Người dùng có thể hoàn toàn yên tâm khi sử dụng các dịch vụ, bởi mọi giao dịch và thông tin cá nhân đều được bảo vệ chặt chẽ. Sự cam kết về độ tin cậy này là một phần quan trọng làm nên uy tín của 188BET.
Ngoài ra, 188BET còn chú trọng xây dựng một cộng đồng trực tuyến sôi động và gắn kết. Nền tảng khuyến khích sự tương tác và kết nối giữa các thành viên, tạo nên một không gian thân thiện và hỗ trợ. Bằng cách lắng nghe ý kiến và nhu cầu của người dùng, 188BET không ngừng cải thiện để mang lại giá trị thiết thực và thúc đẩy sự phát triển chung. Đây là nơi mọi người có thể cùng nhau chia sẻ và tận hưởng các trải nghiệm kỹ thuật số hàng đầu.
Tóm lại, 188BET không chỉ là một nền tảng kỹ thuật số mà còn là một đối tác đáng tin cậy trong hành trình khám phá công nghệ hiện đại. Với sự kết hợp hoàn hảo giữa thiết kế, bảo mật và tương tác cộng đồng, 188BET đã tạo nên một môi trường trải nghiệm hoàn hảo cho người dùng. Nền tảng này không ngừng đổi mới để đáp ứng nhu cầu đa dạng và mang lại những giá trị vượt trội, khẳng định vị thế dẫn đầu trong thế giới kỹ thuật số.
-
 @ 266815e0:6cd408a5
2024-05-09 17:23:28
@ 266815e0:6cd408a5
2024-05-09 17:23:28Lot of people are starting to talk about building a web-of-trust and how nostr can or is already being used as such
We all know about using the kind:3 following lists as a simple WoT that can be used to filter out spam. but as we all know it does not really signal "trust", its mostly just "I find your content interesting"
But what about real "trust"... well its kind of multi-denominational, I could trust that your a good developer or a good journalist but still not trust you enough to invite you over to my house. There are some interesting and clever solutions proposed for quantifying "trust" in a digital sense but I'm not going to get into that here. I want to talk about something that I have not see anyone discuss yet.
How is the web-of-trust maintained? or more precisely how do you expect users to update the digital representation of the "trust" of other users?
Its all well and good to think of how a user would create that "trust" of another user when discovering them for the first time. They would click the "follow" button, or maybe even rate them on a few topics with a 1/5 star system But how will a user remove that trust? how will they update it if things change and they trust them less?
If our goal is to model "trust" in a digital sense then we NEED a way for the data to stay up-to-date and as accurate as possible. otherwise whats the use? If we don't have a friction-less way to update or remove the digital representation of "trust" then we will end up with a WoT that continuously grows and everyone is rated 10/10
In the case of nostr kind:3 following lists. its pretty easy to see how these would get updated. If someone posts something I dislike or I notice I'm getting board of their content. then I just unfollow them. An important part here is that I'm not thinking "I should update my trust score of this user" but instead "I'm no longer interested, I don't want to see this anymore"
But that is probably the easiest "trust" to update. because most of us on social media spend some time curating our feed and we are used to doing it. But what about the more obscure "trust" scores? whats the regular mechanism by which a user would update the "honestly" score of another user?
In the real world its easy, when I stop trusting someone I simply stop associating with them. there isn't any button or switch I need to update. I simply don't talk to them anymore, its friction-less But in the digital realm I would have to remove or update that trust. in other words its an action I need to take instead of an action I'm not doing. and actions take energy.
So how do we reflect something in the digital world that takes no-energy and is almost subconscious in the real world?
TLDR; webs-of-trust are not just about scoring other users once. you must keep the score up-to-date
-
 @ 8d34bd24:414be32b
2024-12-22 15:04:23
@ 8d34bd24:414be32b
2024-12-22 15:04:23We are in the season of Christmas and busy fulfilling all of our Christmas traditions. We put up Christmas decorations, sing Christmas songs, buy Christmas presents, and plan big Christmas meals, but we are supposed to be celebrating the birth of Christ. We are supposed to be celebrating God made flesh — our Creator becoming His creation to reconcile them to Himself.
If you care about your relationship with Jesus, you may wonder, “Are all of these Christmas traditions good or bad?” In most cases, I think the answer is “It depends.” Are you using Christmas traditions to celebrate Jesus and point yourself and others to Him or have the traditions themselves become the focus?
Let’s look at some Christmas traditions and see how we might use them to point us to Jesus instead of distracting us from Him.
Christmas Music
1And suddenly there appeared with the angel a multitude of the heavenly host praising God and saying,
“Glory to God in the highest,\ And on earth peace among men with whom He is pleased.” (Luke 2:13-14)
There is a lot of Christmas music to choose from, but some is more honoring to God than others. Do you spend your time listening to songs like “Jingle Bell Rock,” “Grandma Got Run Over By a Reindeer,” “Baby It’s Cold Outside,” or “I Saw Mommy Kissing Santa Claus” or do you spend your time listening to songs like “O Holy Night,” “O Come, O Come Emmanuel,” “Little Town of Bethlehem,” or “Mary Did You Know?” There isn’t anything inherently wrong with the first type, but the second type is much more honoring to Jesus and will focus our minds on what Jesus did for us.
By listening to Christmas music that points us to Jesus, we honor Him, refocus our own lives, and point others to Him. When we listen to Christmas music that focuses on Santa, Frosty, Rudolph, or just the season of winter, we distract people from the true meaning of Christmas. Listening to Bing Crosby singing “White Christmas” isn’t a problem (and I enjoy it very much), but focus on the Christmas Carols that point us to Jesus. You won’t regret it.
Christmas Decorations (Lights)
Then Jesus again spoke to them, saying, “I am the Light of the world; he who follows Me will not walk in the darkness, but will have the Light of life.” (John 8:12)
I love Christmas decorations and especially Christmas lights. I’ll admit it. This year we even decided we are going to leave the lights up through January because the lights are so cheerful during the dark part of the year when we spend so much time in darkness. The question we should ask ourselves is “Are we just focused on the decorations and lights or are we focused on Jesus?”
Jesus is the Light of the World. He is the light in the darkness. It is appropriate to use lights to celebrate Jesus, but do we focus on the lights or are the lights focusing our thoughts on Jesus? My new Christmas resolution is to remember to thank Jesus for being the light of the world every time I look at the Christmas lights.
Let your light shine before men in such a way that they may see your good works, and glorify your Father who is in heaven. (Matthew 5:16)
Are your Christmas decorations things that point to Jesus or things that point to human tradition like Santa, reindeer, Frosty, etc.? We should aim to have more of our decorations point to Jesus.
Another thing I’ve noticed is that many of our Christian decorations can even be based on tradition rather than actual Biblical inerrancy. Most nativity sets have 3 wise men. Although this error isn’t something to get legalistic about, it is something to be aware of.
Now after Jesus was born in Bethlehem of Judea in the days of Herod the king, magi from the east arrived in Jerusalem, saying, (Matthew 2:1)
Traditionally the magi have been called wise men, but nobody knows 100% who the magi were. They also assume there were 3 of them because of the 3 gifts of gold, frankincense, and myrrh. Based on the uproar that they caused in Jerusalem, it was probably a huge caravan. You’ll also notice that they arrived in Jerusalem “after Jesus was born in Bethlehem.” They then consulted King Herod. King Herod consulted the Jewish leaders to figure out that the Messiah was expected to be born in Bethlehem, and then they traveled to Bethlehem to find Jesus. It isn’t clear how long after Jesus’s birth the Magi showed up, but they definitely weren’t there that first Christmas morning.
Because of this, my husband sets up our main nativity set (that his parents got in Israel) in our living room and sets up the 3 wise men and the camel in our guest bedroom (on the East side of the house). It is his way of supporting the true Christmas story and not just the traditions of men.
Our Christmas tree isn’t just stuff relating to Jesus and the Christmas story. Most of our tree decorations are things for which we are thankful to Jesus. We have ornaments with family pictures. We have handmade ornaments made by the women of our church that were given to us when our house burnt down. We have ornaments from most of the trips we have gone on. We have a few sentimental family ornaments that were given to us when my husband’s mom died. Every time I look at my tree, I am grateful for all of these things. They aren’t just generic decorations. They are memories. I also have an ornament with a picture of my son’s teacher’s autistic son who snuck away and was killed in a blizzard. Every time I see the ornament, I pray for his family who misses him so much. I’d like to think that this tree of blessings is honoring to my God and my Savior.
Christmas Dinner
For I received from the Lord that which I also delivered to you, that the Lord Jesus in the night in which He was betrayed took bread; and when He had given thanks, He broke it and said, “This is My body, which is for you; do this in remembrance of Me.” In the same way He took the cup also after supper, saying, “This cup is the new covenant in My blood; do this, as often as you drink it, in remembrance of Me.” For as often as you eat this bread and drink the cup, you proclaim the Lord’s death until He comes. (1 Corinthians 11:23-26) {emphasis mine}
This passage is about the Passover celebration and Jesus’s command to celebrate the Lord’s Supper in remembrance of Him. I think it is likewise appropriate to celebrate His birth with a meal. As in most things, what makes it honoring to Jesus is how we do Christmas dinner rather than whether we do it or not.
The below passage is about celebrating the Lord’s supper in an inappropriate way, but I will try to apply it to Christmas dinner.
Therefore when you meet together, it is not to eat the Lord’s Supper, for in your eating each one takes his own supper first; and one is hungry and another is drunk. What! Do you not have houses in which to eat and drink? Or do you despise the church of God and shame those who have nothing? What shall I say to you? Shall I praise you? In this I will not praise you. (1 Corinthians 11:20-22)
Is Christmas dinner just about stuffing ourselves with good food or is it about more? Is it about fellowship with friends and family? Is it about gratefulness for what Jesus did for us? Is it about benefitting others?
For most of our marriage, we have alternated celebrating Christmas at my parent’s house and my husband’s parents house, but a couple of times recently, due to different circumstances, we have celebrated Christmas in our own home, and we will be doing it again this year. We’ll celebrate with my family after Christmas, and we celebrated with my husband’s family at Thanksgiving.
Our new tradition is to invite some people over to join us for Christmas dinner if we are celebrating at our home. We invite people from our church that are an older couple with no family nearby, a widow, or a single that is not near family. We invite people who would not have much of a celebration on their own. It has been such a blessing being able to bless others who don’t have family, are in financial hardship, or have physical trouble cooking a big meal.
Whether you are fellowshipping with family or ministering to those who have less than you, Christmas dinner can definitely be a God honoring part of your Christmas traditions.
Christmas Presents
Now He who supplies seed to the sower and bread for food will supply and multiply your seed for sowing and increase the harvest of your righteousness; you will be enriched in everything for all liberality, which through us is producing thanksgiving to God. For the ministry of this service is not only fully supplying the needs of the saints, but is also overflowing through many thanksgivings to God. Because of the proof given by this ministry, they will glorify God for your obedience to your confession of the gospel of Christ and for the liberality of your contribution to them and to all, while they also, by prayer on your behalf, yearn for you because of the surpassing grace of God in you. Thanks be to God for His indescribable gift! (2 Corinthians 9:10-15) {emphasis mine}
Too often we can get so obsessed with the buying and receiving of gifts that we forget the greatest gift of all — the gift of our Savior Jesus.
My 17 year old son has Down Syndrome. He really likes gifts, especially electronics, like tablets, radios, and phones. Unfortunately, he also isn’t very gentle with them and usually has broken or lost most of them by the time Christmas comes along. This often leads to him obsessing about the gifts that he thinks he deserves.
When we celebrated Christmas with my husband’s family at Thanksgiving, he got a nice keyboard that he had requested. He did not, however, get the radio or tablet he wanted. As we were driving home he demanded, “Where is my radio? Where is my tablet? Where is it?” Instead of being grateful for his very generous gift, a gift that he requested, he was upset that he hadn’t gotten everything he wanted. He focused on stuff and not people. He focused on receiving and not giving. He focused on earthly things instead of Jesus. Too often we all do.
But the free gift is not like the transgression. For if by the transgression of the one the many died, much more did the grace of God and the gift by the grace of the one Man, Jesus Christ, abound to the many. The gift is not like that which came through the one who sinned; for on the one hand the judgment arose from one transgression resulting in condemnation, but on the other hand the free gift arose from many transgressions resulting in justification. For if by the transgression of the one, death reigned through the one, much more those who receive the abundance of grace and of the gift of righteousness will reign in life through the One, Jesus Christ. (Romans 5:15-17) {emphasis mine}
Just as Jesus gave His life for us, it is good for us to give to others, but we always need to have the gift giving process be focused on Jesus and not the stuff. We always need to be thankful for what we have and receive and not what we don’t have and haven’t received.
On Christmas morning, before opening gifts, we always read the Christmas story from Luke 2 and the story of the magi from Matthew 2. We then sing “Happy Birthday” to Jesus, to remind us all of the purpose of Christmas and of the greatest gift we have received. I’m also wanting to start a new tradition at Christmas: Before each person opens a gift, they must thank Jesus for one blessing in their life. I think this will change the focus from greed and getting to gratefulness for what we have already received.
For by grace you have been saved through faith; and that not of yourselves, it is the gift of God; not as a result of works, so that no one may boast. For we are His workmanship, created in Christ Jesus for good works, which God prepared beforehand so that we would walk in them. For by grace you have been saved through faith; and that not of yourselves, it is the gift of God; not as a result of works, so that no one may boast. For we are His workmanship, created in Christ Jesus for good works, which God prepared beforehand so that we would walk in them. (Ephesians 2:8-9) {emphasis mine}
Jesus gave us His all. We also need to consider what we can give to those who can’t give back, just as we can’t ever repay Jesus for what He did for us. Is there a family you know that is having a rough year financially or health wise that you could bless with a meal or gifts or help with bills? Is there a charity that will share the gospel and meet the physical needs of those who are alone, broke, and addicted that you can donate to? Maybe your kids have lots of toys and are about to get more and you can donate some that are in good condition to a Christian charity that can get those toys to kids who won’t receive any. Maybe money is tight, but you could volunteer at a soup kitchen or do some yard chores for a widow. I don’t know your personal circumstances or the circumstances of where you are and those around you, but think about finding some way to bless someone less fortunate than you.
Above all, keep fervent in your love for one another, because love covers a multitude of sins. Be hospitable to one another without complaint. As each one has received a special gift, employ it in serving one another as good stewards of the manifold grace of God. Whoever speaks, is to do so as one who is speaking the utterances of God; whoever serves is to do so as one who is serving by the strength which God supplies; so that in all things God may be glorified through Jesus Christ, to whom belongs the glory and dominion forever and ever. Amen. (1 Peter 4:8-11) {emphasis mine}
There are lots of movies, songs, and TV shows that talk about the spirit of Christmas and the love of Christmas. Let’s make sure we show love and share Jesus with the people around us. They tend to be much more open to Jesus during Christmas. Let’s make sure we make the most of Christmas.
To God be the Glory!
Trust Jesus.
FYI, Because everyone is busy at Christmas, I will be posting my short Wednesday post (Christmas) on Tuesday evening (Christmas Eve) so that people can have time to read the post before Christmas and it will hopefully help you to have the right mindset on Christmas.
FYI, to learn more about my books “Why I Need Jesus” (available in paperback and ebook) and “Joy in the Storm” (in editing and hopefully out in a month or two.) see my books page.
-
 @ a012dc82:6458a70d
2024-12-19 03:48:56
@ a012dc82:6458a70d
2024-12-19 03:48:56Table Of Content
-
Who is Michael Burry?
-
Burry's Recent Move and its Implications
-
Bitcoin's Recent Performance and Future Prospects
-
The Broader Economic Context
-
Conclusion
-
FAQ
In the ever-evolving world of cryptocurrencies, the name Michael Burry might not be the first that comes to mind. However, recent developments have thrust him into the spotlight, making many in the crypto community sit up and take notice. So, what's all the fuss about Michael Burry's stance on Bitcoin's price?
Who is Michael Burry?
For those unfamiliar, Michael Burry is an American investor renowned for his prediction of the 2008 subprime mortgage crisis, which led to a global recession. His foresight and investment strategies during that period were so notable that they were depicted in the movie "The Big Short."
Burry's Recent Move and its Implications
Recently, a filing with the US Securities and Exchanges Commission (SEC) revealed that Scion Asset Management, a firm associated with Burry, has taken a significant bearish position on the US stock markets. Specifically, the firm has placed bets predicting a decline in major stock indices, including the Nasdaq 100 and the S&P 500. The numbers are staggering: $740 million worth of Invesco QQQ Trust Series 1 puts and $900 million worth of S&P 500 puts. These bets constitute about 93% of Burry's total portfolio value.
Now, you might wonder, what does this have to do with Bitcoin? The connection lies in the potential ripple effects of these bets. If the US stock market does experience a decline, as Burry seems to anticipate, it could lead to a bullish run for Bitcoin. The reasoning behind this is that traders might view Bitcoin as a high-risk, high-reward investment alternative to traditional stocks.
Bitcoin's Recent Performance and Future Prospects
Bitcoin has been experiencing a prolonged sideways movement, testing the patience of many traders. Historically, such sideways movements in the crypto market have sometimes been followed by a significant jump in value. Additionally, there's growing optimism about the potential approval of a Bitcoin ETF in the coming months, which could further boost its price.
The Broader Economic Context
In understanding Burry's moves and their potential impact on Bitcoin, it's essential to consider the broader economic landscape. The U.S. central bank, the Federal Reserve, is currently in a position where they might not increase the interest rate in the upcoming September FOMC meeting, as gauged by the CME FedWatch Tool. Historically, low-interest rates have often led to increased investment in riskier assets, as investors search for higher returns. This environment could further bolster the appeal of cryptocurrencies like Bitcoin, especially if traditional stock markets become more volatile or start to decline.
Furthermore, other global events, such as the US regional bank crisis that erupted earlier in 2023, have shown that Bitcoin can sometimes act as a hedge or alternative investment during times of traditional market stress. As such, the broader economic context, combined with Burry's predictions, paints a fascinating picture for Bitcoin's potential trajectory in the near future.
Conclusion
While Michael Burry's recent moves primarily concern the US stock market, the potential implications for the crypto market, and Bitcoin in particular, are significant. If Burry's predictions come to fruition, and the US stock market sees a decline, it could be a pivotal moment for Bitcoin and its investors. As always, the world of investments is unpredictable, but with big names like Burry making such moves, it's an exciting time for observers and participants alike.
FAQ
Who is Michael Burry? Michael Burry is an American investor known for predicting the 2008 subprime mortgage crisis. He was prominently featured in the movie "The Big Short."
What has Burry recently predicted about the US stock market? Burry's firm, Scion Asset Management, has placed significant bets predicting a decline in major US stock indices, including the Nasdaq 100 and the S&P 500.
How might Burry's predictions affect Bitcoin's price? If the US stock market declines as Burry anticipates, it could lead to a bullish run for Bitcoin, with traders viewing it as a high-risk, high-reward alternative to stocks.
What is the broader economic context influencing Bitcoin? The Federal Reserve's potential decision not to increase interest rates, combined with global events like the US regional bank crisis, could influence Bitcoin's appeal as an alternative investment.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 07804b78:c375c543
2024-12-15 12:56:05
@ 07804b78:c375c543
2024-12-15 12:56:05Japanese follows. 日本語はあとで。
This article is for the 14th day of Nostr Advent Calendar 2024 (relay blogging). The article for the 13th day was "Open Sats 申請編" (Applying for Open Sats) by mono-san. The article for the 14th day will be "Nostrはじめました。" (I started Nostr) by bro-san.
Thinking of Thingstr
I've come up with an idea for Other Staff that I think is interesting (at least, for me), so I'm going to write about it. I actually wanted to show you the implementation and brag about it, but it's not solid enough to be implemented yet.
The key idea is just “add a reaction to the WikiData ID”.
WikiData
There is a service called WikiData. It is a knowledge base that provides structured data. You may be wondering what it is, but the important thing to understand here is that WikiData assigns identifiers to a fairly wide range of “objects” and “things”.
So, if you can react to this, you can think of various applications just by thinking of it for a moment, right?
For example, the anime series “There are too many losing heroines!” is assigned the ID
Q123819103. The corresponding page is https://www.wikidata.org/wiki/Q123819103 .(NOTE: The canonical URI for entities on Wikidata is http://www.wikidata.org/entity/Q1142841. This is in accordance with Semantic Web conventions, and is not https, but http. Also, this URI does not necessarily match the actual address of the correspnding web page. Just an identifier. In most cases, it will redirect).
What can wd do?
For example, what about a website that records your anime viewing history? You can record what you want to watch with 👀, what you've already watched with ✅, and your favorites with ☆. You can also express your “likes” for production companies, staff, voice actors, etc. In this way, you can see what a particular user likes.
This could be a movie, a book, a comic, an author, music, an idol group, a place, or food (Someone likes pork cutlet
Q1142841). The fact that you can record everything in the same framework is what makes it interesting.What form of event should it be recorded as?
There is probably room for discussion about how to record this information in a concrete way. The simplest way would be to use NIP-25's "Reactions to a website" kind:17 (a.k.a. Makibishi). How about something like this?
json [ ["i", "wd:Q123819103", "http://www.wikidata.org/entity/Q123819103"], ]Since NIP-73 has External Content IDs, it would be good if we could include WikiData here so that we could write
wd:Q123819103. Actually,isbn:and other identifiers have already been defined, so it is possible to use the current NIP range to describe books (however, the authors do not have IDs. If we use WikiData as an ID, we can also describe reactions related to the author). Of course, it is not a matter of choosing one or the other, and it is also fine to add the ISBN tag at the same time as the WikiData tag for books.Search for recorded reactions
So far, this is all very simple, but it would be inconvenient if we didn't include tags to mark subsets of reactions (for example, only those related to anime) so that we can query them together. When we try to create a site that is specialized for a certain purpose, we need to be able to extract the reactions that are necessary.
On Wikidata, the predicate
wdt:P31(instance of) is used to group together concepts that represent the same thing. For example, how about including this in theltag? "There are too many losing heroines!" is a "Japanese television anime series (Q63952888)", so:json [ ["i", "wd:Q1142841", "http://www.wikidata.org/entity/Q1142841"], ["l", "wdt:P31 wd:Q63952888"] ]UPDATE(2024-12-15): rnurachue-san suggested that
#lor#Lmight be better for labeling (the first version used#a). I think that's a good idea, so I've updated the article. nostr:nevent1qgswamu0rsela0kwhj87p24ueapxdp04vzz7ar0pp6lfyq923t3l02cqyr9786635s60ra0f973nwv2sln2l74lqx4twdlgxfz2jgevpvsgtc9zwn6dHowever, when you think about creating an anime website, you may want to query both TV anime and anime films. This makes things more complicated. "Japanese TV anime series (
Q63952888)" is a subclass (subclass of;wdt:P279) of "Anime series (Q117467261)", which is in turn a subclass of "Anime (Q1107)". However, if you were to embed this hierarchy in each reaction, it would waste a lot of space. The following query will get all the superclasses of "Japanese TV anime series (Q63952888)", but there are 54 of them.https://query.wikidata.org/#%23%20Subclass%20hierarchy%20traversal%20for%20Q63952888%0ASELECT%20%3Fitem%20%3FitemLabel%20%3Fsuperclass%20%3FsuperclassLabel%0AWHERE%20%7B%0A%20%20%23%20Starting%20class%0A%20%20wd%3AQ63952888%20wdt%3AP279%2a%20%3Fsuperclass%20.%0A%20%20BIND%28wd%3AQ63952888%20AS%20%3Fitem%29%0A%20%20SERVICE%20wikibase%3Alabel%20%7B%20bd%3AserviceParam%20wikibase%3Alanguage%20%22%5BAUTO_LANGUAGE%5D%2Cen%22.%20%7D%0A%7D%0AORDER%20BY%20%3Fsuperclass%0A
So, I think it should be okay for practical purposes to embed
P31s of the reaction target. In other words, if you search for "anime seriesQ63952888" and "anime movieQ20650540", that should be enough. Fortunately, the conditions for single-character tags work with OR, so you can query multiple tags at once. we'll have to try it to see how well it works in practice, though.Discussion: Which kind should I use?
So far we have considered using kind:17, but we have not yet decided whether it is a good idea to mix Thingstr events with reactions to web pages.
Also, there may be a debate over whether to record regular events or addressable events, depending on the purpose of use. For example, if you want to record the transition of viewing results and impressions on an anime viewing site, you should use regular events, and if you want to maintain the viewing status, you should use addressable events.
What do you think?
Other ideas
If we can react to Nodes on OpenStreetMap using the same framework, we might be able to create something like Swarm. Since the views you want to see will differ depending on the purpose, it would be good to create various sites while having a consistent way of recording. Wouldn't that be the most Nostr-like thing?
Summary
I discussed how to use WikiData and OpenStreetMap as an ID infrastructure and realize various check-in and review services with a unified data model by using them on Nostr. Please let us know if you have any feedback. Or why not try implementing it?
この記事は Nostr Advent Calendar 2024 の14日目の記事です。13日目の記事はmonoさんによる「Open Sats 申請編」でした。15日目の記事はbroさんによる「Nostrはじめました。」です。
Thingstrについて考えた
面白そうな(と勝手に思ってる) Other Staff のアイディアを思いついたので、書いてみます。 本当は実装を持ってきて自慢したかったのですが、まだふわっとしていて実装に落ちていません。
コアになるアイディアは「WikiData の ID に対して、Reactionをつける」これだけです。
WikiData
WikiData というサービスがあります。構造化データを提供する知識ベースです。 なにそれ?という感じですが、ここで大事なのはWikiDataはかなり広範な「もの」「こと」に識別子(Identifier)を付与している、ということです。
だから、これにリアクションできれば、ぱっと思いつくだけでもいろいろな応用ができそうじゃないですか。
例えば、アニメシリーズ「負けヒロインが多すぎる!」には
Q123819103というIDが振られています。これに対応するページとして https://www.wikidata.org/wiki/Q123819103 があります。(ただし、WikiData のエンティティに対する canonical な URI は http://www.wikidata.org/entity/Q1142841 であることには注意が必要です。セマンティックウェブの作法で https ではなく http になっています。そして、このURIは必ずしもWebページのアドレス一致しません。大抵の場合はリダイレクトされます)。
なにができるの
たとえば、アニメの視聴記録サイトはどうでしょう。👀は見たい作品、✅は視聴済み、☆はお気に入り、みたいに記録していく。制作会社、スタッフ、声優、...に対してLikeを表明したりできそうです。そうすると、あるユーザが何にLikeしているかわかります。
これが映画でもいいし、書籍、漫画、作家でもいいし、音楽でもいいし、アイドルグループでもいいし、場所でもいいし、食べ物でもいい(とんかつ
Q1142841が好き、とか)。全部同じ枠組みで記録できるのが面白そうなところです。どういうNostrイベントで記録する?
具体的な記録の仕方には議論の余地があるでしょう。一番単純なのは、NIP-25の "Reactions to a website" kind:17 (Makibishi) を使う方法でしょうか。こんなのはどうでしょう。
json [ ["i", "wd:Q123819103", "http://www.wikidata.org/entity/Q123819103"], ]NIP-73にExternal Content IDsがあるので、ここにWikiDataを入れられるようにして
wd:Q123819103と書けるとよさそうです。実はisbn:などはすでに定義されているので、書籍に関しては現行のNIPの範囲でもうまいことできます(ただ、著者にはIDが振られていません。WikiDataをIDに使うと著者に関するリアクションも記述できます)。もちろん、どちらか一方を選ぶというものでもなくて、書籍にはWikiDataのタグと当時にISBNのタグを付与しておいてもいいと思います。記録されたリアクションを検索する
ここまではシンプルでよいのですが、リアクションの部分集合(たとえばアニメに関連するものだけ、とか)をまとめてクエリできるように、目印となるタグを入れておかないと不便です。ある目的に特化したサイトを作ろうとしたとき、必要になるリアクションが抽出できるようにしておかないといけません。
WikiData では
wdt:P31(instance of) という述語で、ある概念が何を表しているかをグルーピングしてくれています。例えばこれをlタグとかに含めておくのはどうでしょうか。負けヒロインが多すぎる!は「日本のテレビアニメシリーズ(
Q63952888)」なので、json [ ["i", "wd:Q1142841", "http://www.wikidata.org/entity/Q1142841"], ["l", "wdt:P31 wd:Q63952888"] ]みたいな感じで付与します。
UPDATE(2024-12-15): rnurachueさんからラベル付けには
#lまたは#Lのほうがよいかもという提案をいただきました。最初のバージョンでは#aを使用していました。そのとおりだと思ったので更新しました。 nostr:nevent1qgswamu0rsela0kwhj87p24ueapxdp04vzz7ar0pp6lfyq923t3l02cqyr9786635s60ra0f973nwv2sln2l74lqx4twdlgxfz2jgevpvsgtc9zwn6dただ、アニメサイトを作ることを考えると、テレビアニメも劇場版アニメも両方クエリしたいこともありそうですよね。そうなると話が複雑になってきます。
「日本のテレビアニメシリーズ(
Q63952888)」は「アニメシリーズ(Q117467261)」のサブクラス(subclass of;wdt:P279)で、それがさらに「アニメ(Q1107)」 のサブクラスになっています。ただ、この階層をいちいちリアクションに埋め込むのと大変なことになります。以下のようなクエリで「日本のテレビアニメシリーズ(Q63952888)」のすべての上位クラスが取れるのですが、54件もあります。https://query.wikidata.org/#%23%20Subclass%20hierarchy%20traversal%20for%20Q63952888%0ASELECT%20%3Fitem%20%3FitemLabel%20%3Fsuperclass%20%3FsuperclassLabel%0AWHERE%20%7B%0A%20%20%23%20Starting%20class%0A%20%20wd%3AQ63952888%20wdt%3AP279%2a%20%3Fsuperclass%20.%0A%20%20BIND%28wd%3AQ63952888%20AS%20%3Fitem%29%0A%20%20SERVICE%20wikibase%3Alabel%20%7B%20bd%3AserviceParam%20wikibase%3Alanguage%20%22%5BAUTO_LANGUAGE%5D%2Cen%22.%20%7D%0A%7D%0AORDER%20BY%20%3Fsuperclass%0A
なので、リアクション対象の
P31を埋め込む、くらいで実用上は問題ないような気がします。つまり、検索するときに 「アニメシリーズQ63952888」と「アニメ映画Q20650540」を対象にすれば、十分では、ということです。幸い、一文字タグの条件はORで効くので、複数を並べて一度にクエリできます。実際にどのくらいうまく行くかはやってみないとわからないですが。議論: どの kind を使うべきか?
一旦 kind 17 を使うことを考えてきましたが、Thingstr のイベントが Web ページに対するリアクションと混ざるのが良いことなのか、いまいち判断がついていません。
また、用途によって regular event で記録するべきか、それとも addressable event で記録すべきか、という議論もありそうです。 アニメ視聴サイトを例にあげるなら、視聴実績とか感想の変遷を記録したいならば regular event でしょうし、視聴の状態を保持したいならば addressable とするのがよさそうです。
どう思いますか?
他のアイディア
これと同じ枠組みで OpenStreetMap の Node に対してリアクションできるようにすれば Swarm のようなものも実現できるかもしれません。
用途ごとに見たいビューは違うだろうから、一貫した記録の仕方を持ちつつ、色々なサイトを作ったらいいんじゃないでしょうか。それって最高にNostrっぽくないですか?
まとめ
WikiDataやOpenStreetMapをID基盤として活用し、Nostr上でreactすることで、様々なチェックインサービス、レビューサービスを統一的なデータモデルで実現する方法について議論しました。フィードバックがあったら教えてください。むしろ実装してみてください。
-
 @ fd208ee8:0fd927c1
2024-12-20 06:58:48
@ fd208ee8:0fd927c1
2024-12-20 06:58:48When the shit just don't work
Most open-source software is now so badly written and sloppily-maintained, that it's malware.
That's why the governments are getting involved. They try using OS, to save money and improve quality (and to market themselves as "hip"), and then it blows up their system or opens them up to hackers.
Now, they're pissed and want support (but the dev with the handle SucksToBeYou has disappeared) or someone to sue, but most OS projects have no identifiable entity behind them. Even well-known anon devs are often groups of anons or accounts that change hands.
The software cracks have moved on
There is simply no evidence that OS alone produces higher-quality software. The reason it seemed that way, at the beginning, was because of the caliber of the developers working on the projects, and the limited number of projects. This resulted in experienced people actively reviewing each others' code.
OS used to be something the elite engaged in, but it's mostly beginners practicing in public, now. That's why there are now millions of OS projects, happily offered for free, but almost all of them are garbage. The people now building OS usually aren't capable of reviewing other people's code, and they're producing worse products than ChatGPT could. Their software has no customers because it has no market value.
If everything is OS, then nothing is.
Another paradigm-changer is that all software is de facto OS, now that we can quickly reverse-engineer code with AI. That means the focus is no longer on OS/not-OS, but on the accountability and reputation of the builders.
It is, once again, a question of trust. We have come full-circle.
-
 @ 266815e0:6cd408a5
2024-04-22 22:20:47
@ 266815e0:6cd408a5
2024-04-22 22:20:47While I was in Mediera with all the other awesome people at the first SEC cohort there where a lot of discussions around data storage on nostr and if it could be made censorship-resistent
I remember lots of discussions about torrents, hypercore, nostr relays, and of course IPFS
There were a few things I learned from all these conversations:
- All the existing solutions have one thing in common. A universal ID of some kind for files
- HTTP is still good. we don't have to throw the baby out with the bath water
- nostr could fix this... somehow
Some of the existing solutions work well for large files, and all of them are decentralization in some way. However none of them seem capable of serving up cat pictures for social media clients. they all have something missing...
An Identity system
An identity system would allow files to be "owned" by users. and once files have owners servers could start grouping files into a single thing instead of a 1000+ loose files
This can also greatly simplify the question of "what is spam" for a server hosting (or seeding) these files. since it could simply have a whitelist of owners (and maybe their friends)
What is blossom?
Blossom is a set of HTTP endpoints that allow nostr users to store and retrieve binary data on public servers using the sha256 hash as a universal id
What are Blobs?
blobs are chunks of binary data. they are similar to files but with one key difference, they don't have names
Instead blobs have a sha256 hash (like
b1674191a88ec5cdd733e4240a81803105dc412d6c6708d53ab94fc248f4f553) as an IDThese IDs are universal since they can be computed from the file itself using the sha256 hashing algorithm ( you can get a files sha256 hash on linux using:
sha256sum bitcoin.pdf)How do the servers work?
Blossom servers expose four endpoints to let clients and users upload and manage blobs
GET /<sha256>(optional file.ext)PUT /uploadAuthentication: Signed nostr event- Returns a blob descriptor
GET /list/<pubkey>- Returns an array of blob descriptors
Authentication(optional): Signed nostr eventDELETE /<sha256>Authentication: Signed nostr event
What is Blossom Drive?
Blossom Drive is a nostr app built on top of blossom servers and allows users to create and manage folders of blobs
What are Drives
Drives are just nostr events (kind
30563) that store a map of blobs and what filename they should have along with some extra metadataAn example drive event would be
json { "pubkey": "266815e0c9210dfa324c6cba3573b14bee49da4209a9456f9484e5106cd408a5", "created_at": 1710773987, "content": "", "kind": 30563, "tags": [ [ "name", "Emojis" ], [ "description", "nostr emojis" ], [ "d", "emojis" ], [ "r", "https://cdn.hzrd149.com/" ], [ "x", "303f018e613f29e3e43264529903b7c8c84debbd475f89368cb293ec23938981", "/noStrudel.png", "15161", "image/png" ], [ "x", "a0e2b39975c8da1702374b3eed6f4c6c7333e6ae0008dadafe93bd34bfb2ca78", "/satellite.png", "6853", "image/png" ], [ "x", "e8f3fae0f4a43a88eae235a8b79794d72e8f14b0e103a0fed1e073d8fb53d51f", "/amethyst.png", "20487", "image/png" ], [ "x", "70bd5836807b916d79e9c4e67e8b07e3e3b53f4acbb95c7521b11039a3c975c6", "/nos.png", "36521", "image/png" ], [ "x", "0fc304630279e0c5ab2da9c2769e3a3178c47b8609b447a30916244e89abbc52", "/primal.png", "29343", "image/png" ], [ "x", "9a03824a73d4af192d893329bbc04cd3798542ee87af15051aaf9376b74b25d4", "/coracle.png", "18300", "image/png" ], [ "x", "accdc0cdc048f4719bb5e1da4ff4c6ffc1a4dbb7cf3afbd19b86940c01111568", "/iris.png", "24070", "image/png" ], [ "x", "2e740f2514d6188e350d95cf4756bbf455d2f95e6a09bc64e94f5031bc4bba8f", "/damus.png", "32758", "image/png" ], [ "x", "2e019f08da0c75fb9c40d81947e511c8f0554763bffb6d23a7b9b8c9e8c84abb", "/old emojis/astral.png", "29365", "image/png" ], [ "x", "d97f842f2511ce0491fe0de208c6135b762f494a48da59926ce15acfdb6ac17e", "/other/rabbit.png", "19803", "image/png" ], [ "x", "72cb99b689b4cfe1a9fb6937f779f3f9c65094bf0e6ac72a8f8261efa96653f5", "/blossom.png", "4393", "image/png" ] ] }There is a lot going on but the main thing is the list of "x" tags and the path that describes the folder and filename the blob should live at
If your interested, the full event definition is at github.com/hzrd149/blossom-drive
Getting started
Like every good nostr client it takes a small instruction manual in order to use it properly. so here are the steps for getting started
1. Open the app
Open https://blossom.hzrd149.com
2. Login using extension

You can also login using any of the following methods using the input - NIP-46 with your https://nsec.app or https://flare.pub account - a NIP-46 connection string - an
ncryptsecpassword protected private key - ansecunprotected private key (please don't) - bunker:// URI from nsecbunker3. Add a blossom server

Right now
https://cdn.satellite.earthis the only public server that is compatible with blossom drive. If you want to host your own I've written a basic implementation in TypeScript github.com/hzrd149/blossom-server4. Start uploading your files
NOTE: All files upload to blossom drive are public by default. DO NOT upload private files

5. Manage files

Encrypted drives
There is also the option to encrypt drives using NIP-49 password encryption. although its not tested at all so don't trust it, verify

Whats next?
I don't know, but Im excited to see what everyone else on nostr builds with this. I'm only one developer at the end of the day and I can't think of everything
also all the images in this article are stored in one of my blossom drives here
nostr:naddr1qvzqqqrhvvpzqfngzhsvjggdlgeycm96x4emzjlwf8dyyzdfg4hefp89zpkdgz99qq8xzun5d93kcefdd9kkzem9wvr46jka
-
 @ a012dc82:6458a70d
2024-12-18 07:07:01
@ a012dc82:6458a70d
2024-12-18 07:07:01Table Of Content
-
A New Dawn in Energy and Digital Asset Collaboration
-
The DEC: A Nexus for Constructive Dialogue
-
Support from the Corridors of Power
-
Harnessing the Power of Innovation for a Sustainable Future
-
Conclusion
-
FAQ
In today's rapidly evolving digital age, the synergy between energy and digital asset mining, especially Bitcoin, is becoming increasingly significant. Enter the Digital Energy Council (DEC), a pioneering organization that has taken the bold step to bridge this gap.
A New Dawn in Energy and Digital Asset Collaboration
The DEC has made its grand entrance as the first member association with a laser focus on the crossroads of energy security and digital asset mining. Their mission? To lead the charge in crafting policies that not only promote responsible energy practices but also bolster the resilience of our energy grids. This is all with the aim of ensuring the United States remains at the forefront of this revolution, safeguarding national security.
Tom Mapes, the Founder and President of the Digital Energy Council, highlighted a crucial point. While most discussions around digital assets have revolved around financial services, the potential collaboration between digital asset mining and the energy sector has been somewhat overshadowed. Yet, this collaboration is vital, especially at this crucial juncture of energy transformation.
The DEC: A Nexus for Constructive Dialogue
Envisioning itself as a central hub, the DEC aims to foster meaningful conversations among its members, policymakers, and regulators. One of its primary goals is to clear the air on various misconceptions surrounding digital asset mining, U.S. energy security, and the modernization of our energy grids.
Moreover, the DEC is not just about discussions and policies. They're action-oriented. Their initiatives are geared towards spurring economic growth in often-neglected communities, including those in rural areas. How? By creating lucrative job opportunities in markets that haven't traditionally been associated with such roles.
Support from the Corridors of Power
The DEC's efforts haven't gone unnoticed. U.S. Senator Lisa Murkowski, who led the first-ever hearing on the implications of digital asset mining for energy supply back in 2018, is among the first to join hands with the DEC. She emphasized how this burgeoning industry has expanded its footprint across the U.S. over the past five years, bringing fresh opportunities to states like Alaska.
Echoing her sentiments, U.S. Senator from Wyoming, Cynthia Lummis, stated that crypto asset mining is poised to play a pivotal role in the financial future of the next generation of Americans. She believes that innovative mining technologies can tap into underutilized energy sources, creating jobs in rural America and generating wealth.
Harnessing the Power of Innovation for a Sustainable Future
The fusion of energy and digital asset mining is not just about economic growth or technological advancement. At its core, it's about sustainability. As the world grapples with the challenges of climate change and energy conservation, the role of organizations like the Digital Energy Council becomes even more paramount.
The DEC recognizes the potential of digital asset mining, especially in the realm of Bitcoin, to revolutionize the way we think about energy consumption. By tapping into innovative mining technologies, we can harness underutilized energy sources, reduce wastage, and pave the way for a more sustainable future.
Furthermore, the emphasis on rural America is not just about job creation. It's about ensuring that every corner of the nation benefits from this synergy, ensuring a balanced and inclusive growth trajectory. As we move forward, the collaboration between sectors, as championed by the DEC, will be instrumental in shaping a future that's not only prosperous but also sustainable.
Conclusion
The Digital Energy Council is more than just an organization. It's a movement. A movement that seeks to harmonize responsible energy practices with the world of digital asset mining. As we stand on the cusp of a new era, the DEC's efforts promise a brighter future, one where the nation's growth, security, and prosperity are at the heart of every initiative.
FAQs
What is the Digital Energy Council (DEC)? The DEC is the first member association focused on the intersection of energy security and digital asset mining.
What is the primary mission of the DEC? The DEC aims to spearhead policies that promote responsible energy practices, enhance grid resilience, and ensure the competitive edge and national security of the United States.
Why is the synergy between energy and digital asset mining important? This synergy is crucial for fostering responsible energy practices, bolstering energy infrastructure, and supporting energy sustainability and efficiency.
How does the DEC plan to dispel misconceptions around digital asset mining? The DEC envisions itself as a hub for facilitating productive discourse among its members, policymakers, and regulators, focusing on themes like U.S. energy security, sustainability, and grid modernization.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 4dffec17:4c4cbd48
2024-12-20 03:06:46
@ 4dffec17:4c4cbd48
2024-12-20 03:06:46Why Are Cryptocurrencies Important? Cryptocurrencies are changing the world for several reasons:
- Decentralization: They remove the need for banks, giving users more control.
- Security: Blockchain ensures secure, tamper-proof transactions.
- Financial Inclusion: Cryptos give financial access to people without traditional bank accounts.
- Innovation: Technologies like smart contracts and DeFi are reshaping industries. By breaking barriers and reducing costs, cryptocurrencies are paving the way for a more inclusive and transparent financial future.
Next: Explore the benefits of using cryptocurrency!
-
 @ 5af07946:98fca8c4
2024-12-22 14:05:19
@ 5af07946:98fca8c4
2024-12-22 14:05:19On the surface, it appears the contest is between the
old guardand thenew innovation.Old seeks to maintain a status quo to ensure a safe passage of their knowledge (wealth) to the new. And the new knows the old as a dependable trustee. The shift, however, must happen, and it needs a trigger - something unwarranted - a mishap to break the umbilical cord. Bigger the ensuing shift, bigger the mishap.
In a way, the mishap marks the beginning of the transition - start of a new time. It is a gun shot to initialize the race. The battle begins at this moment amongst many variants of "new". In fact, many new possibilities crop up to capitalize the opportunity. Having recognized the inevitable, they all stake their claim to being righteous and thus the earnest representation of truth. This happens over and over again as in "history repeats itself". There are many examples[^history] in our recent past though a keen observers may see them in their own backyard.
They occur for the consciousness must evolve to understand the nature of unity[^unit] - the smallest common factor. A mishap is thus a mere setback before the hitherto slow breeding innovations sling into top gear. Such triggers, driven by imperceptible evolution of consciousness are said to be caused by
Prarbdha.Prarbdha, aSanskritword, means something that had already begun. It ties together the past, present and the future - the continuumBramh. In that it also means "fate", because the fate had commenced before the material event physically occurred.[^history]: Battles between old and new in recent history: - IBM was the old. Microsoft and Apple battled for superiority in computing as contenders for new leadership title. For an observes in late 80s it appeared as if big blue is fighting Apple (and later Microsoft) but that was just a trigger. The real battle was between Apple and Microsoft. - Laptop was old, the newcomers iOS and Android are battling for superiority in mobile computing. For quite some time it felt like mobile devices were the PC killers, but the truth is battle is never between the old and the new. It is always among many new contenders. - It appears as big oil is at odds with the EVs or the hydrogen fuel cells. Though the truth is fossil fuel industry will be the biggest investors in sustainable future - because they know first hand about the shift. Sustainable energy is the opportunity for refiners because someone needs to do the work, and they are best positioned to take advantage of this massive opportunity. The real battle is among Solar, Wind , Nuclear and Hydrogen. - Gold is old. It appears that bitcoin is trying to replace Gold. But that is not true. The real battle is with in Cryptos - BTC vs Ether vs Sol vs so many other possibilities. When the dust settles, we will see Gold has its own role to play just like laptop has its own role to play in the increasingly mobile world.
[^unit]: A unit is an immutable part of any measurement. Easy examples - a meter is an immutable unit of length. A kilo is an immutable unit of weight. A unit is part of every measurement - it lends meaning to what is being measured - it is implicit in what is being measured. It is a multiplication that outputs exactly what is being measured. - Little harder example - Number “1” is the unit of multiplication itself. It is there inbuilt into every number (even zero) . It never changes the number when multiplied -> a unit when multiplied with what is being measured , must stay inert - never change the measurement ! But you can't measure anything without a unit … no number exists without "1" - Hard question - What is the unit of consciousness ? By definition, it must be 1) immutable 2) part of every conscious being. 3) must stay inert. - In
Vaidikscience ,Atmais defined as the unit of consciousness. It is immutable, inert and essential. For humans, understandingAtmais as hard as understanding number 1 for say number 8. -
 @ 20986fb8:cdac21b3
2024-12-18 03:41:09
@ 20986fb8:cdac21b3
2024-12-18 03:41:09中文
介绍 YakiHonne:创作无极限
YakiHonne 是一款终极文本编辑器,旨在帮助您无论使用何种语言都能创意表达。
您会喜欢的功能:
- 🌟 丰富的格式:支持添加标题、加粗、斜体等多种格式。
- 🌏 多语言支持:轻松书写英文、中文、阿拉伯语和日语内容。
- 🔗 互动链接:了解更多关于 YakiHonne。优势:
1. 易于使用。
2. 可定制样式以增强可读性。
3. 支持多种复杂格式,包括 LateX。“YakiHonne 为内容创作者带来了颠覆性的改变。”
-
 @ 4685f3d6:9fe6995b
2024-12-20 00:17:35
@ 4685f3d6:9fe6995b
2024-12-20 00:17:35Bitcoin vs. Traditional Money: Bitcoin and fiat currencies serve as mediums of exchange but differ fundamentally.
Key Differences Control: Bitcoin is decentralized, while fiat is regulated by governments and central banks. Supply: Bitcoin has a limited supply (21 million coins), while fiat can be printed indefinitely. Form: Bitcoin exists digitally, whereas fiat is both physical and digital. Transaction Speed and Fees: Bitcoin offers faster, cheaper global transactions compared to fiat's slower and costlier systems. Transparency and Accessibility: Bitcoin is transparent and inclusive, while fiat can be opaque and regulated.
Pros of Bitcoin Decentralized, borderless, and resistant to inflation. Provides financial inclusion and transaction transparency. Cons of Bitcoin
Highly volatile, less universally accepted, and energy-intensive. Requires internet and technical knowledge to use effectively. Pros of Fiat Stable, widely accepted, and backed by governments. Offers consumer protections and ease of use. Cons of Fiat Inflation risk, high transaction costs, limited privacy, and susceptibility to government control. Conclusion
Bitcoin is revolutionary but not yet a full replacement for fiat. It complements traditional money by offering new possibilities for global and financial freedom.
bitcoin
9ja
afro
yakihonne
-
 @ 42342239:1d80db24
2024-12-22 09:07:27
@ 42342239:1d80db24
2024-12-22 09:07:27Knappheit statt Slogans: eine Dosis ökonomischer Realität für die politischen Debatten
Die EU-Wirtschaft steht vor zahlreichen Herausforderungen, von hohen Energiekosten bis hin zu geringer Produktivität. Doch hinter der offiziellen Rhetorik verbirgt sich eine Annahme, die kaum hinterfragt wird: dass der grüne Wandel automatisch zu Wirtschaftswachstum und mehr Wohlstand führen wird. Aber stimmt das wirklich?
Eine englische Fassung dieses Textes finden Sie hier.
In Deutschland, das wieder einmal das Etikett „Kranker Mann Europas" tragen muss, kämpft Bundeskanzler Olaf Scholz vor der Wahl im Februar mit alarmierend niedrigen Vertrauenswerten. Aber vielleicht ist das gar nicht so überraschend. ****Die deutsche Industrieproduktion ist rückläufig, seit die grüne Agenda in Mode gekommen ist. ****Die energieintensive Produktion ist in nur wenigen Jahren um ganze 20 Prozent zurückgegangen. Volkswagen schließt Fabriken, Thyssenkrupp entlässt massiv Mitarbeiter und mehr als drei Millionen Rentner sind von Armut bedroht .
Wenn dies Europas „Mann auf dem Mond"-Moment ist, wie EU-Kommissarin von der Leyen ****es 2019 ausdrückte ****, dann ist das nicht viel, womit man angeben kann . Zumindest nicht, wenn man kein Sadist ist.
Der Bericht des ehemaligen EZB-Chefs Mario Draghi über die Wettbewerbsfähigkeit der EU wurde bereits früher diskutiert. Eines der Probleme, auf die hingewiesen wurde, war, dass europäische Unternehmen erheblich höhere Energiekosten haben als ihre amerikanischen Konkurrenten. Die Strompreise sind zwei- bis dreimal so hoch und die Erdgaspreise vier- bis fünfmal so hoch.
Deutschland ist vielleicht am schlimmsten dran, was zum Teil an der Entscheidung der ehemaligen Bundeskanzlerin Angela Merkel liegt, vollständig aus der Atomkraft auszusteigen (eine Entscheidung, die nicht nur keine breite Unterstützung fand , sondern die sie auch nicht als Fehler eingestehen will). Die Sabotage der Nord Stream 2 hat die Situation noch verschlimmert.
Ohne Realkapital kein wirtschaftlicher Wohlstand
Der Ausstieg aus der Atomenergie in Deutschland ist ein Beispiel dafür, wie politische Entscheidungen zur Verringerung der Kapazität der Wirtschaft beigetragen haben. Dasselbe gilt für die Sabotage der Nord Stream. Realkapital, wie Gebäude, Maschinen und Ausrüstung, ist für die Produktivität der Wirtschaft von entscheidender Bedeutung (z. B. Kennzahlen wie das BIP pro Arbeitsstunde). Ein größerer und effizienterer Kapitalstock ermöglicht die Herstellung von mehr Waren und Dienstleistungen mit der gleichen Menge an Arbeit, was zu mehr Produktion, höheren Löhnen und größerem materiellen Wohlstand führt. Das ist grundlegende Ökonomie. ****Wenn andererseits Realkapital aufgrund politischer Entscheidungen für obsolet erklärt wird, wie im Fall der Abschaltung der Atomkraft, verringert dies die Kapazität der Wirtschaft. ****Dasselbe gilt, wenn Realkapital zerstört wird, wie dies bei Nord Stream der Fall war.
Weiteres reales Betriebskapital wird zurückgestellt
EU-Kommissarin von der Leyen verspricht Besserung. Sie scheint überzeugt, dass der Niedergang der EU durch eine Verdreifachung der grünen Ziele des Blocks umgekehrt werden kann, und hat die Dekarbonisierung als eine der drei wichtigsten Säulen eines neuen „Wettbewerbsfähigkeitskompasses" aufgeführt. Wenn die Realität nicht den Erwartungen entspricht, kann man immer noch „Strg+Alt+Slogan" drücken und hoffen, dass niemand merkt, dass sich nichts verbessert hat.
Ihre Pläne bedeuten jedoch, dass bestehendes und derzeit funktionierendes Realkapital in Zukunft in noch größerem Umfang abgeschrieben wird. Dies lässt sich mit einer Nation vergleichen, die Jahr für Jahr ihre Naturschutzgebiete schrittweise erweitert. Tatsächlich geschieht dies auch. Der Kunming-Montreal-Rahmen für die Artenvielfalt sieht vor, dass bis 2030 30 % aller Flächen an Land und im Meer geschützt werden müssen. Ein Land, das derzeit weniger schützt, muss daher zusätzliche Gebiete identifizieren, die geschützt werden können. ****Der Prozess, 30 % aller Flächen zu schützen, wird wahrscheinlich das Produktionspotenzial der Wirtschaft verringern. ****Mit schrumpfenden Feldern wird es weniger Karotten geben (es sei denn, es werden bedeutende technologische Fortschritte erzielt).
Konsequenzen für Sicherheitspolitik und -vorsorge
Auf dem derzeitigen Weg wird mehr Realkapital auf die lange Bank geschoben, was weitreichende Folgen haben kann, nicht zuletzt für unsere Sicherheitspolitik. Wenn Russland beispielsweise Artilleriegeschosse etwa dreimal schneller produzieren kann, und zwar zu Kosten, die etwa ein Viertel der Kosten betragen, die die westlichen Verbündeten der Ukraine dafür aufbringen , dann ist klar, dass dies sicherheitspolitische Konsequenzen hat. Ebenso wird es negative sicherheitspolitische Konsequenzen haben, wenn die Strompreise in Deutschland fünfmal höher sind als in China, was derzeit der Fall ist . Im Vergleich zur EU hat China tatsächlich einen höheren Kohlendioxidausstoß pro Kopf, wobei der Unterschied den ****verfügbaren Daten zufolge etwa 50 % beträgt ****. Bereinigt um den internationalen Handel emittiert China pro Kopf 10 % mehr als Schweden .
Auch eine Perspektive der Vorsorge ist zu finden. Anfang der 1990er Jahre produzierten schwedische Landwirte fast 75 % der Nahrungsmittel des Landes. Heute ist Schwedens Bevölkerung deutlich gewachsen, aber die Nahrungsmittelproduktion hat nicht Schritt gehalten. Jeder zweite Bissen wird heute importiert. In Schweden können wir uns sogar rühmen, dass wir uns nicht einmal mit der einfachsten aller Feldfrüchte versorgen können -- Kartoffeln . Können wir wirklich sicher sein, dass deutlich erweiterte Naturschutzgebiete, wie sie im Kunming-Montreal-Rahmenwerk für Schweden vorgeschrieben sind, unsere Nahrungsmittelvorsorge nicht noch weiter verschlechtern werden?
Erinnert an kleine Gnome
Ich erinnere mich an eine Folge der 90er-Jahre-Serie South Park, in der kleine Gnome Unterhosen sammeln . Als sie nach ihrem Plan gefragt wurden, beschrieben sie ihre Methode:
- Unterhosen sammeln
- ???
- profitieren!
Übersetzt auf die grüne **Energiewende **:
- reales Kapital zerstören und Land und Meer erhalten
- ???
- wirtschaftlicher Wohlstand!
Was kann sich die EU wirklich leisten?
In der Wirtschaft geht es im Grunde um die Verwaltung knapper Ressourcen, was viele Menschen offenbar vergessen haben. Es ist höchste Zeit, zu hinterfragen, was sich die EU wirklich leisten kann. Können wir es uns wirklich leisten, uns für einen Krieg gegen Russland, China und den Iran zu rüsten und uns gleichzeitig mit grünen Versprechen von reduzierten Kohlendioxidemissionen und erhöhter Artenvielfalt selbst die Hände zu binden? Und das in einer Situation, in der die nächste US-Regierung wahrscheinlich massiv in die Steigerung ihrer Wettbewerbsvorteile durch Deregulierung, niedrigere Energiepreise, Steuersenkungen und einen Rückzug aus dem Pariser Abkommen investieren wird ?
Als von der Leyen für das deutsche Militär verantwortlich war, sei die Lage " katastrophal " gewesen. Alle sechs U-Boote des Landes waren außer Gefecht gesetzt . Zeitweise war kein einziges der 14 Transportflugzeuge des Landes flugfähig. Bei Übungen mussten deutsche Soldaten Besen statt Gewehren verwenden .
Hoffentlich wird von der Leyen in ihrem Umgang mit der Wirtschaft, der Verteidigung und der Abwehrbereitschaft der EU mehr Erfolg zeigen als in ihrer Rolle als deutsche Verteidigungsministerin. Es könnte jedoch auch an der Zeit sein, dass mehr Menschen die vorherrschenden Narrative, die unsere Politik prägen, in Frage stellen. Was, wenn die Fakten nicht ganz mit der Wahrheit übereinstimmen, die uns erzählt wird?
-
 @ 7ed7d5c3:6927e200
2024-12-18 00:56:48
@ 7ed7d5c3:6927e200
2024-12-18 00:56:48There was a time when we dared not rustle a whisper. But now we write and read samizdat and, congregating in the smoking rooms of research institutes, heartily complain to each other of all they are muddling up, of all they are dragging us into! There’s that unnecessary bravado around our ventures into space, against the backdrop of ruin and poverty at home; and the buttressing of distant savage regimes; and the kindling of civil wars; and the ill-thought-out cultivation of Mao Zedong (at our expense to boot)—in the end we’ll be the ones sent out against him, and we’ll have to go, what other option will there be? And they put whomever they want on trial, and brand the healthy as mentally ill—and it is always “they,” while we are—helpless.
We are approaching the brink; already a universal spiritual demise is upon us; a physical one is about to flare up and engulf us and our children, while we continue to smile sheepishly and babble:
“But what can we do to stop it? We haven’t the strength.”
We have so hopelessly ceded our humanity that for the modest handouts of today we are ready to surrender up all principles, our soul, all the labors of our ancestors, all the prospects of our descendants—anything to avoid disrupting our meager existence. We have lost our strength, our pride, our passion. We do not even fear a common nuclear death, do not fear a third world war (perhaps we’ll hide away in some crevice), but fear only to take a civic stance! We hope only not to stray from the herd, not to set out on our own, and risk suddenly having to make do without the white bread, the hot water heater, a Moscow residency permit.
We have internalized well the lessons drummed into us by the state; we are forever content and comfortable with its premise: we cannot escape the environment, the social conditions; they shape us, “being determines consciousness.” What have we to do with this? We can do nothing.
But we can do—everything!—even if we comfort and lie to ourselves that this is not so. It is not “they” who are guilty of everything, but we ourselves, only we!
Some will counter: But really, there is nothing to be done! Our mouths are gagged, no one listens to us, no one asks us. How can we make them listen to us?
To make them reconsider—is impossible.
The natural thing would be simply not to reelect them, but there are no re-elections in our country.
In the West they have strikes, protest marches, but we are too cowed, too scared: How does one just give up one’s job, just go out onto the street?
All the other fateful means resorted to over the last century of Russia’s bitter history are even less fitting for us today—true, let’s not fall back on them! Today, when all the axes have hewn what they hacked, when all that was sown has borne fruit, we can see how lost, how drugged were those conceited youths who sought, through terror, bloody uprising, and civil war, to make the country just and content. No thank you, fathers of enlightenment! We now know that the vileness of the means begets the vileness of the result. Let our hands be clean!
So has the circle closed? So is there indeed no way out? So the only thing left to do is wait inertly: What if something just happens by itself?
But it will never come unstuck by itself, if we all, every day, continue to acknowledge, glorify, and strengthen it, if we do not, at the least, recoil from its most vulnerable point.
From lies.
When violence bursts onto the peaceful human condition, its face is flush with self-assurance, it displays on its banner and proclaims: “I am Violence! Make way, step aside, I will crush you!” But violence ages swiftly, a few years pass—and it is no longer sure of itself. To prop itself up, to appear decent, it will without fail call forth its ally—Lies. For violence has nothing to cover itself with but lies, and lies can only persist through violence. And it is not every day and not on every shoulder that violence brings down its heavy hand: It demands of us only a submission to lies, a daily participation in deceit—and this suffices as our fealty.
And therein we find, neglected by us, the simplest, the most accessible key to our liberation: a personal nonparticipation in lies! Even if all is covered by lies, even if all is under their rule, let us resist in the smallest way: Let their rule hold not through me!
And this is the way to break out of the imaginary encirclement of our inertness, the easiest way for us and the most devastating for the lies. For when people renounce lies, lies simply cease to exist. Like parasites, they can only survive when attached to a person.
We are not called upon to step out onto the square and shout out the truth, to say out loud what we think—this is scary, we are not ready. But let us at least refuse to say what we do not think!
This is the way, then, the easiest and most accessible for us given our deep-seated organic cowardice, much easier than (it’s scary even to utter the words) civil disobedience à la Gandhi.
Our way must be: Never knowingly support lies! Having understood where the lies begin (and many see this line differently)—step back from that gangrenous edge! Let us not glue back the flaking scales of the Ideology, not gather back its crumbling bones, nor patch together its decomposing garb, and we will be amazed how swiftly and helplessly the lies will fall away, and that which is destined to be naked will be exposed as such to the world.
And thus, overcoming our timidity, let each man choose: Will he remain a witting servant of the lies (needless to say, not due to natural predisposition, but in order to provide a living for the family, to rear the children in the spirit of lies!), or has the time come for him to stand straight as an honest man, worthy of the respect of his children and contemporaries? And from that day onward he:
· Will not write, sign, nor publish in any way, a single line distorting, so far as he can see, the truth;
· Will not utter such a line in private or in public conversation, nor read it from a crib sheet, nor speak it in the role of educator, canvasser, teacher, actor;
· Will not in painting, sculpture, photograph, technology, or music depict, support, or broadcast a single false thought, a single distortion of the truth as he discerns it;
· Will not cite in writing or in speech a single “guiding” quote for gratification, insurance, for his success at work, unless he fully shares the cited thought and believes that it fits the context precisely;
· Will not be forced to a demonstration or a rally if it runs counter to his desire and his will; will not take up and raise a banner or slogan in which he does not fully believe;
· Will not raise a hand in vote for a proposal which he does not sincerely support; will not vote openly or in secret ballot for a candidate whom he deems dubious or unworthy;
· Will not be impelled to a meeting where a forced and distorted discussion is expected to take place;
· Will at once walk out from a session, meeting, lecture, play, or film as soon as he hears the speaker utter a lie, ideological drivel, or shameless propaganda;
· Will not subscribe to, nor buy in retail, a newspaper or journal that distorts or hides the underlying facts.
This is by no means an exhaustive list of the possible and necessary ways of evading lies. But he who begins to cleanse himself will, with a cleansed eye, easily discern yet other opportunities.
Yes, at first it will not be fair. Someone will have to temporarily lose his job. For the young who seek to live by truth, this will at first severely complicate life, for their tests and quizzes, too, are stuffed with lies, and so choices will have to be made. But there is no loophole left for anyone who seeks to be honest: Not even for a day, not even in the safest technical occupations can he avoid even a single one of the listed choices—to be made in favor of either truth or lies, in favor of spiritual independence or spiritual servility. And as for him who lacks the courage to defend even his own soul: Let him not brag of his progressive views, boast of his status as an academician or a recognized artist, a distinguished citizen or general. Let him say to himself plainly: I am cattle, I am a coward, I seek only warmth and to eat my fill.
For us, who have grown staid over time, even this most moderate path of resistance will be not be easy to set out upon. But how much easier it is than self-immolation or even a hunger strike: Flames will not engulf your body, your eyes will not pop out from the heat, and your family will always have at least a piece of black bread to wash down with a glass of clear water.
Betrayed and deceived by us, did not a great European people—the Czechoslovaks—show us how one can stand down the tanks with bared chest alone, as long as inside it beats a worthy heart?
It will not be an easy path, perhaps, but it is the easiest among those that lie before us. Not an easy choice for the body, but the only one for the soul. No, not an easy path, but then we already have among us people, dozens even, who have for years abided by all these rules, who live by the truth.
And so: We need not be the first to set out on this path, Ours is but to join! The more of us set out together, the thicker our ranks, the easier and shorter will this path be for us all! If we become thousands—they will not cope, they will be unable to touch us. If we will grow to tens of thousands—we will not recognize our country!
But if we shrink away, then let us cease complaining that someone does not let us draw breath—we do it to ourselves! Let us then cower and hunker down, while our comrades the biologists bring closer the day when our thoughts can be read and our genes altered.
And if from this also we shrink away, then we are worthless, hopeless, and it is of us that Pushkin asks with scorn:
Why offer herds their liberation?
............................. Their heritage each generation
The yoke with jingles, and the whip.February 12, 1974
—translated from the Russian by Yermolai Solzhenitsyn
-
 @ f977c464:32fcbe00
2024-01-30 20:06:18
@ f977c464:32fcbe00
2024-01-30 20:06:18Güneşin kaybolmasının üçüncü günü, saat öğlen on ikiyi yirmi geçiyordu. Trenin kalkmasına yaklaşık iki saat vardı. Hepimiz perondaydık. Valizlerimiz, kolilerimiz, renk renk ve biçimsiz çantalarımızla yan yana dizilmiş, kısa aralıklarla tepemizdeki devasa saati kontrol ediyorduk.
Ama ne kadar dik bakarsak bakalım zaman bir türlü istediğimiz hızla ilerlemiyordu. Herkes birkaç dakika sürmesi gereken alelade bir doğa olayına sıkışıp kalmış, karanlıktan sürünerek çıkmayı deniyordu.
Bekleme salonuna doğru döndüm. Nefesimden çıkan buharın arkasında, kalın taş duvarları ve camlarıyla morg kadar güvenli ve soğuk duruyordu. Cesetleri o yüzden bunun gibi yerlere taşımaya başlamışlardı. Demek insanların bütün iyiliği başkaları onları gördüğü içindi ki gündüzleri gecelerden daha karanlık olduğunda hemen birbirlerinin gırtlağına çökmüş, böğürlerinde delikler açmış, gözlerini oyup kafataslarını parçalamışlardı.
İstasyonun ışığı titrediğinde karanlığın enseme saplandığını hissettim. Eğer şimdi, böyle kalabalık bir yerde elektrik kesilse başımıza ne gelirdi?
İçerideki askerlerden biri bakışlarımı yakalayınca yeniden saate odaklanmış gibi yaptım. Sadece birkaç dakika geçmişti.
“Tarlalarım gitti. Böyle boyum kadar ayçiçeği doluydu. Ah, hepsi ölüp gidiyor. Afitap’ın çiçekleri de gi-”
“Dayı, Allah’ını seversen sus. Hepimizi yakacaksın şimdi.”
Karanlıkta durduğunda, görünmez olmayı istemeye başlıyordun. Kimse seni görmemeli, nefesini bile duymamalıydı. Kimsenin de ayağının altında dolaşmamalıydın; gelip kazayla sana çarpmamalılar, takılıp sendelememeliydiler. Yoksa aslında hedefi sen olmadığın bir öfke gürlemeye başlar, yaşadığın ilk şoku ve acıyı silerek üstünden geçerdi.
İlk konuşan, yaşlıca bir adam, kafasında kasketi, nasırlı ellerine hohluyordu. Gözleri ve burnu kızarmıştı. Güneşin kaybolması onun için kendi başına bir felaket değildi. Hayatına olan pratik yansımalarından korkuyordu olsa olsa. Bir anının kaybolması, bu yüzden çoktan kaybettiği birinin biraz daha eksilmesi. Hayatta kalmasını gerektiren sebepler azalırken, hayatta kalmasını sağlayacak kaynaklarını da kaybediyordu.
Onu susturan delikanlıysa atkısını bütün kafasına sarmış, sakalı ve yüzünün derinliklerine kaçmış gözleri dışında bedeninin bütün parçalarını gizlemeye çalışıyordu. İşte o, güneşin kaybolmasının tam olarak ne anlama geldiğini anlamamış olsa bile, dehşetini olduğu gibi hissedebilenlerdendi.
Güneşin onlardan alındıktan sonra kime verileceğini sormuyorlardı. En başta onlara verildiğinde de hiçbir soru sormamışlardı zaten.
İki saat ne zaman geçer?
Midemin üstünde, sağ tarafıma doğru keskin bir acı hissettim. Karaciğerim. Gözlerimi yumdum. Yanımda biri metal bir nesneyi yere bıraktı. Bir kafesti. İçerisindeki kartalın ıslak kokusu burnuma ulaşmadan önce bile biliyordum bunu.
“Yeniden mi?” diye sordu bana kartal. Kanatları kanlı. Zamanın her bir parçası tüylerinin üstüne çöreklenmişti. Gagası bir şey, tahminen et parçası geveliyor gibi hareket ediyordu. Eski anılar kolay unutulmazmış. Şu anda kafesinin kalın parmaklıklarının ardında olsa da bunun bir aldatmaca olduğunu bir tek ben biliyordum. Her an kanatlarını iki yana uzatıverebilir, hava bu hareketiyle dalgalanarak kafesi esneterek hepimizi içine alacak kadar genişleyebilir, parmaklıklar önce ayaklarımızın altına serilir gibi gözükebilir ama aslında hepimizin üstünde yükselerek tepemize çökebilirdi.
Aşağıya baktım. Tahtalarla zapt edilmiş, hiçbir yere gidemeyen ama her yere uzanan tren rayları. Atlayıp koşsam… Çantam çok ağırdı. Daha birkaç adım atamadan, kartal, suratını bedenime gömerdi.
“Bu sefer farklı,” diye yanıtladım onu. “Yeniden diyemezsin. Tekrarladığım bir şey değil bu. Hatta bir hata yapıyormuşum gibi tonlayamazsın da. Bu sefer, insanların hak etmediğini biliyorum.”
“O zaman daha vahim. Süzme salaksın demektir.”
“İnsanların hak etmemesi, insanlığın hak etmediği anlamına gelmez ki.”
Az önce göz göze geldiğim genççe ama çökük asker hâlâ bana bakıyordu. Bir kartalla konuştuğumu anlamamıştı şüphesiz. Yanımdakilerden biriyle konuştuğumu sanmış olmalıydı. Ama konuştuğum kişiye bakmıyordum ona göre. Çekingence kafamı eğmiştim. Bir kez daha göz göze geldiğimizde içerideki diğer iki askere bir şeyler söyledi, onlar dönüp beni süzerken dışarı çıktı.
Yanımızdaki, az önce konuşan iki adam da şaşkınlıkla bir bana bir kartala bakıyordu.
“Yalnız bu sefer kalbin de kırılacak, Prometheus,” dedi kartal, bana. “Belki son olur. Biliyorsun, bir sürü soruna neden oluyor bu yaptıkların.”
Beni koruyordu sözde. En çok kanıma dokunan buydu. Kasıklarımın üstüne oturmuş, kanlı suratının ardında gözleri parlarken attığı çığlık kulaklarımda titremeye devam ediyordu. Bu tabloda kimsenin kimseyi düşündüğü yoktu. Kartalın, yanımızdaki adamların, artık arkama kadar gelmiş olması gereken askerin, tren raylarının, geçmeyen saatlerin…
Arkamı döndüğümde, asker sahiden oradaydı. Zaten öyle olması gerekiyordu; görmüştüm bunu, biliyordum. Kehanetler… Bir şeyler söylüyordu ama ağzı oynarken sesi çıkmıyordu. Yavaşlamış, kendisini saatin akışına uydurmuştu. Havada donan tükürüğünden anlaşılıyordu, sinirliydi. Korktuğu için olduğunu biliyordum. Her seferinde korkmuşlardı. Beni unutmuş olmaları işlerini kolaylaştırmıyordu. Sadece yeni bir isim vermelerine neden oluyordu. Bu seferkiyle beni lanetleyecekleri kesinleşmişti.
Olması gerekenle olanların farklı olması ne kadar acınasıydı. Olması gerekenlerin doğasının kötücül olmasıysa bir yerde buna dayanıyordu.
“Salaksın,” dedi kartal bana. Zamanı aşan bir çığlık. Hepimizin önüne geçmişti ama kimseyi durduramıyordu.
Sonsuzluğa kaç tane iki saat sıkıştırabilirsiniz?
Ben bir tane bile sıkıştıramadım.
Çantama uzanıyordum. Asker de sırtındaki tüfeğini indiriyordu. Benim acelem yoktu, onunsa eli ayağı birbirine dolaşıyordu. Oysaki her şey tam olması gerektiği anda olacaktı. Kehanet başkasının parmaklarının ucundaydı.
Güneş, bir tüfeğin patlamasıyla yeryüzüne doğdu.
Rayların üzerine serilmiş göğsümün ortasından, bir çantanın içinden.
Not: Bu öykü ilk olarak 2021 yılında Esrarengiz Hikâyeler'de yayımlanmıştır.
-
 @ 0f286a37:601a59e8
2024-12-17 19:56:41
@ 0f286a37:601a59e8
2024-12-17 19:56:41bitcoin #news I encourage every Bitcoiner to read The Blocksize War. Here are all of the links to all 21 chapters available on the BitMEX blog.
- Chapter 1 – First Strike
- Chapter 2 – March To War
- Chapter 3 – Scaling I - Montreal
- Chapter 4 – Scaling II - Hong Kong
- Chapter 5 – SegWit
- Chapter 6 – Lightning Network
- Chapter 7 – Bitcoin Classic
- Chapter 8 – Hong Kong Roundtable
- Chapter 9 – Faketoshi
- Chapter 10 – The DAO
- Chapter 11 – Scaling III – Milan
- Chapter 12 – Bitcoin Unlimited
- Chapter 13 – Exchanges
- Chapter 14 – ASICBoost
- Chapter 15 – Dragons’ Den
- Chapter 16 – Litecoin
- Chapter 17 – User-Activated Softfork
- Chapter 18 – New York Agreement
- Chapter 19 - Bitcoin Cash
- Chapter 20 - SegWit2x
- [Chapter 21 - Victory] https://blog.bitmex.com/the-blocksize-war-chapter-21-victory/)
-
 @ ac8bb9b0:70278acc
2024-12-11 20:10:29
@ ac8bb9b0:70278acc
2024-12-11 20:10:29Details
- ⏲️ Prep time: 15
- 🍳 Cook time: 1 hour 30 minutes
- 🍽️ Servings: 10
Ingredients
- 1 lb. ground beef
- 1 cup celery diced
- 1 cup carrots diced
- 1 medium onion diced
- 2 medium potatoes diced
- 5 cups beef broth
- 1 15 oz. can corn, drained
- 1 8 oz. can tomato sauce
- 1 28 oz. can diced tomatoes
- 1 teaspoon salt
- 1 teaspoon Italian seasoning
- 1 bay leaf
Directions
- In a large dutch oven (I used a 6-quart), over medium heat brown the ground beef until done. Spoon off the excess fat.
- Add the remaining ingredients and stir. Bring to a boil and reduce the heat. Allow to simmer for 1 to 1 ½ hours (with the lid on, but tilted so steam can release) or until the vegetables are tender.
- Remove the bay leaf and serve.
-
 @ 03742c20:2df9aa5d
2024-12-22 04:52:31
@ 03742c20:2df9aa5d
2024-12-22 04:52:31วันนี้เราจะลองมาติดตั้ง Lnbits โดยใช้ funding source เป็น Albyhub ผ่าน NWC
ในบทนี้จะใช้งาน Docker เป็นหลักแต่ก็สามารถทำตามได้ง่าย ๆ
Lnbits
Lnbits คืออะไร open-source lightning wallet ที่มีฟังก์ชั่นมากมายเหมาะสำหรับสายนักพัฒนา ฟิวเจอร์ที่โดดเด่นอย่างระบบ POS ที่ช่วยอำนวยความสะดวกให้กับร้านค้าหรือว่าจะเป็น API ที่นำไปต่อยอดในตู้หยอดเหรียญต่าง ๆ
วิธีติดตั้ง
เราต้องติดตั้ง Albyhub ก่อน
สร้างโฟลเดอร์ Albyhub
mkdir alby-hubเข้าไปในโฟลเดอร์ alby-hubcd alby-hubสร้าง docker-compose.yml ไฟล์nano docker-compose.ymlservices: albyhub: platform: linux/amd64 container_name: albyhub image: ghcr.io/getalby/hub:latest volumes: - ./albyhub-data:/data ports: - "8080:8080" environment: - WORK_DIR=/data/albyhub - LOG_EVENTS=trueสั่งรัน Albyhubsudo docker compose up -dsudo ufw allow 8080/tcp comment 'Allow alby hub’แค่นี้เราได้ Albyhub ใช้งานแล้ว เข้า http://localhost:8080 set-up ให้เรียบร้อย
ซื้อ LSP 2m sat ผมแนะนำของ LNserver ราคาประมาณ 13xxx sat
มาติดตั้ง Lnbits กันต่อ
สร้างโฟลเดอร์ Lnbits
mkdir lnbitsเข้าไปในโฟลเดอร์ Lnbitscd lnbitsดาวน์โหลดไฟล์ .envwget https://raw.githubusercontent.com/lnbits/lnbits/main/.env.example -O .envสร้างโฟลเดอร์เก็บข้อมูลmkdir dataดาวน์โหลด image lnbitsdocker pull lnbits/lnbitsสั่งรัน Lnbitsdocker run --detach --publish 5000:5000 --name lnbits --volume ${PWD}/.env:/app/.env --volume ${PWD}/data/:/app/data lnbits/lnbitssudo ufw allow 5000/tcp comment 'Allow lnbits’แค่นี้ได้ Lnbits ใช้งานแล้ว เข้า http://localhost:5000 set-up ให้เรียบร้อยตั้งค่า funding source ของ Lnbits server > funding > funding source > เลือก Nostr wallet connect
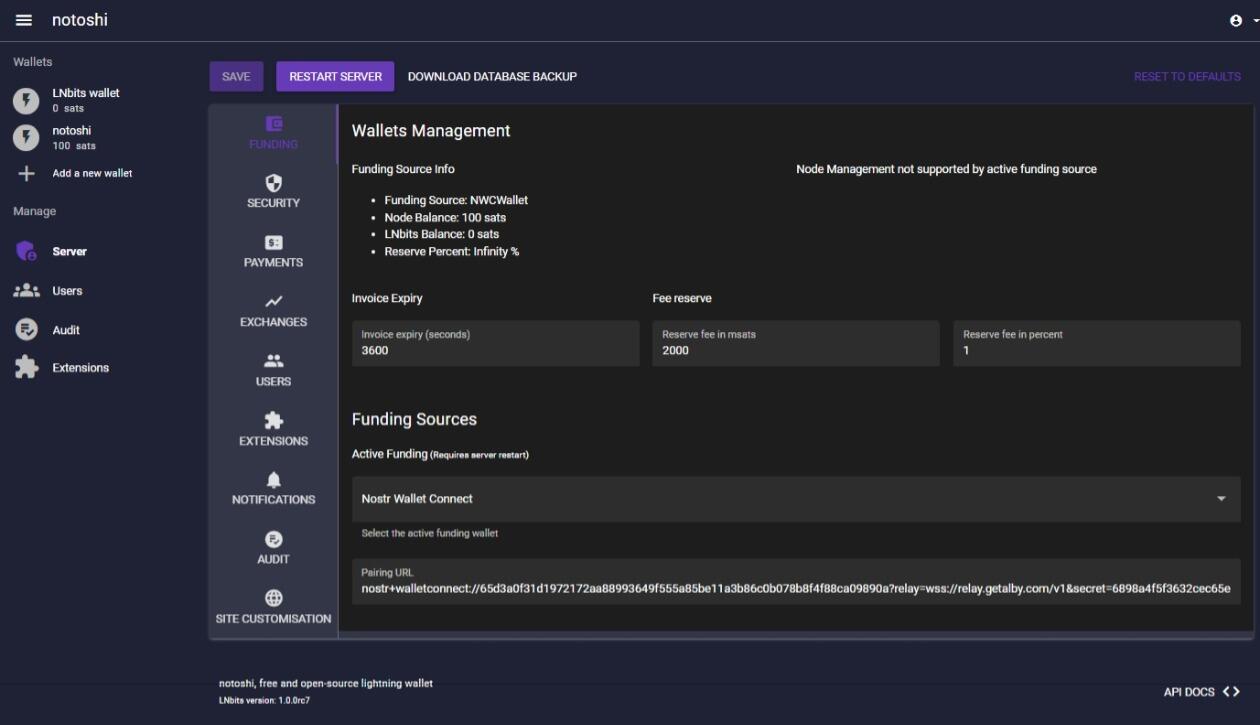
เปิด Albyhub จากนั้นไปที่ App Store เลือก Friends & Family
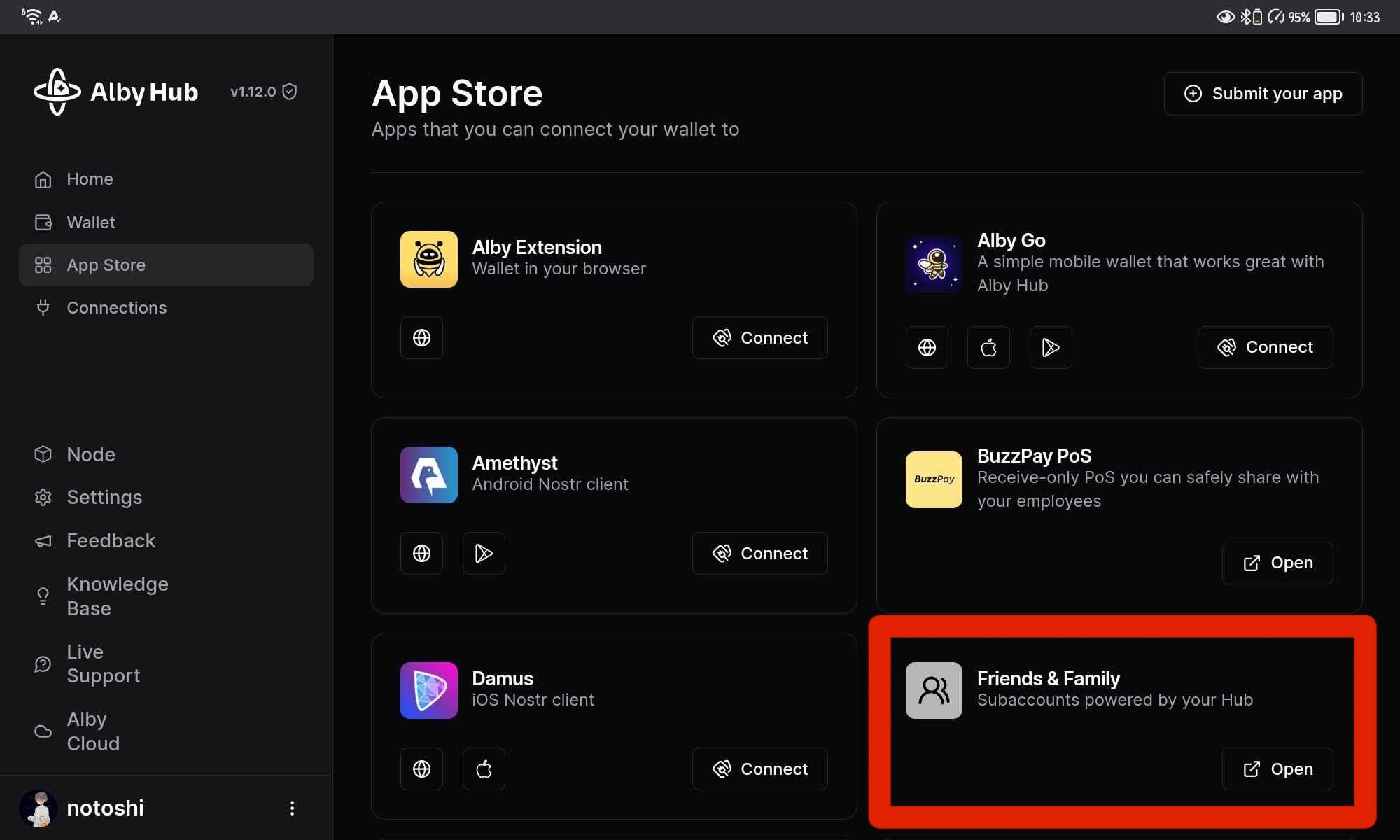
ตั้งชื่อและกดสร้าง Subaccount
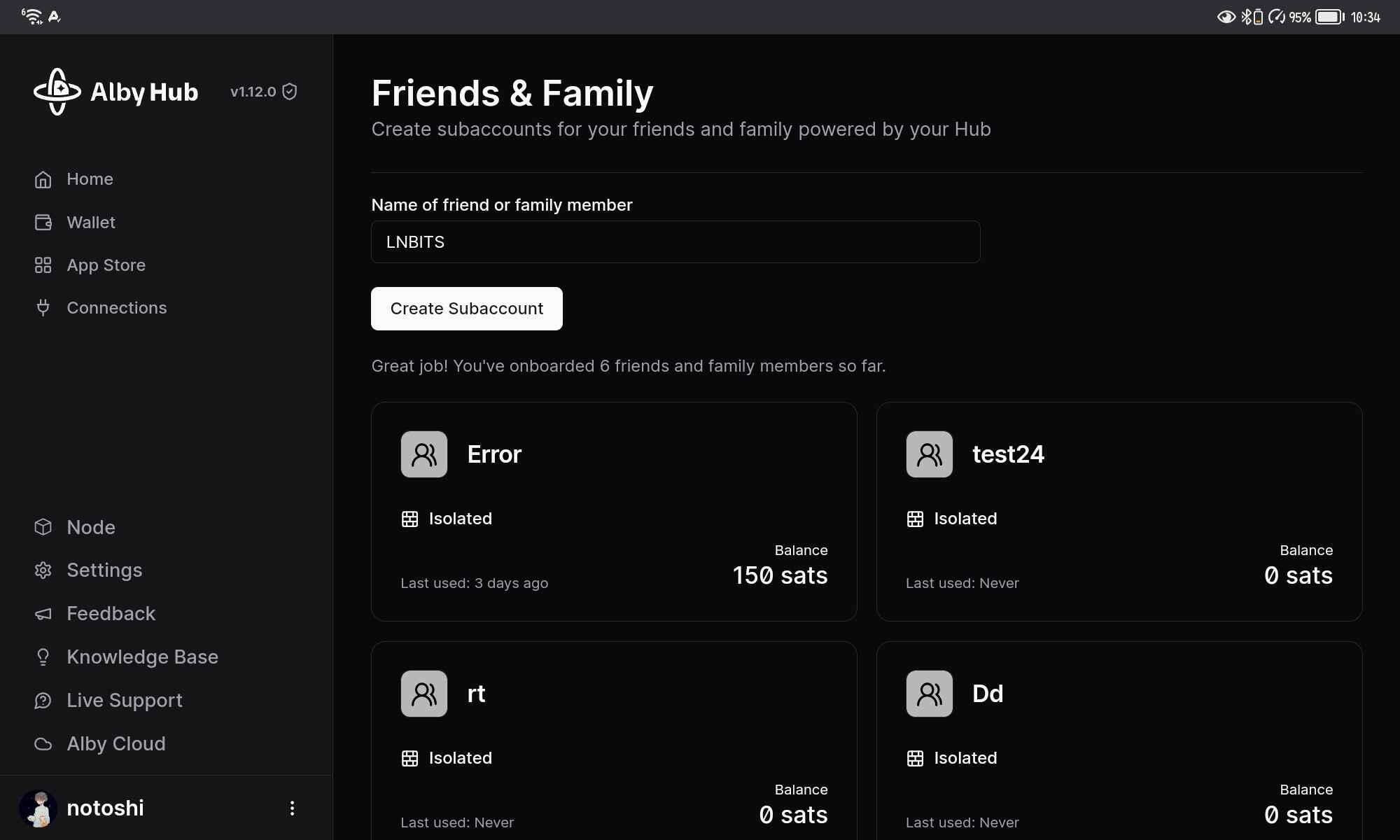
ไปที่ Other NWC applications คลิก Copy
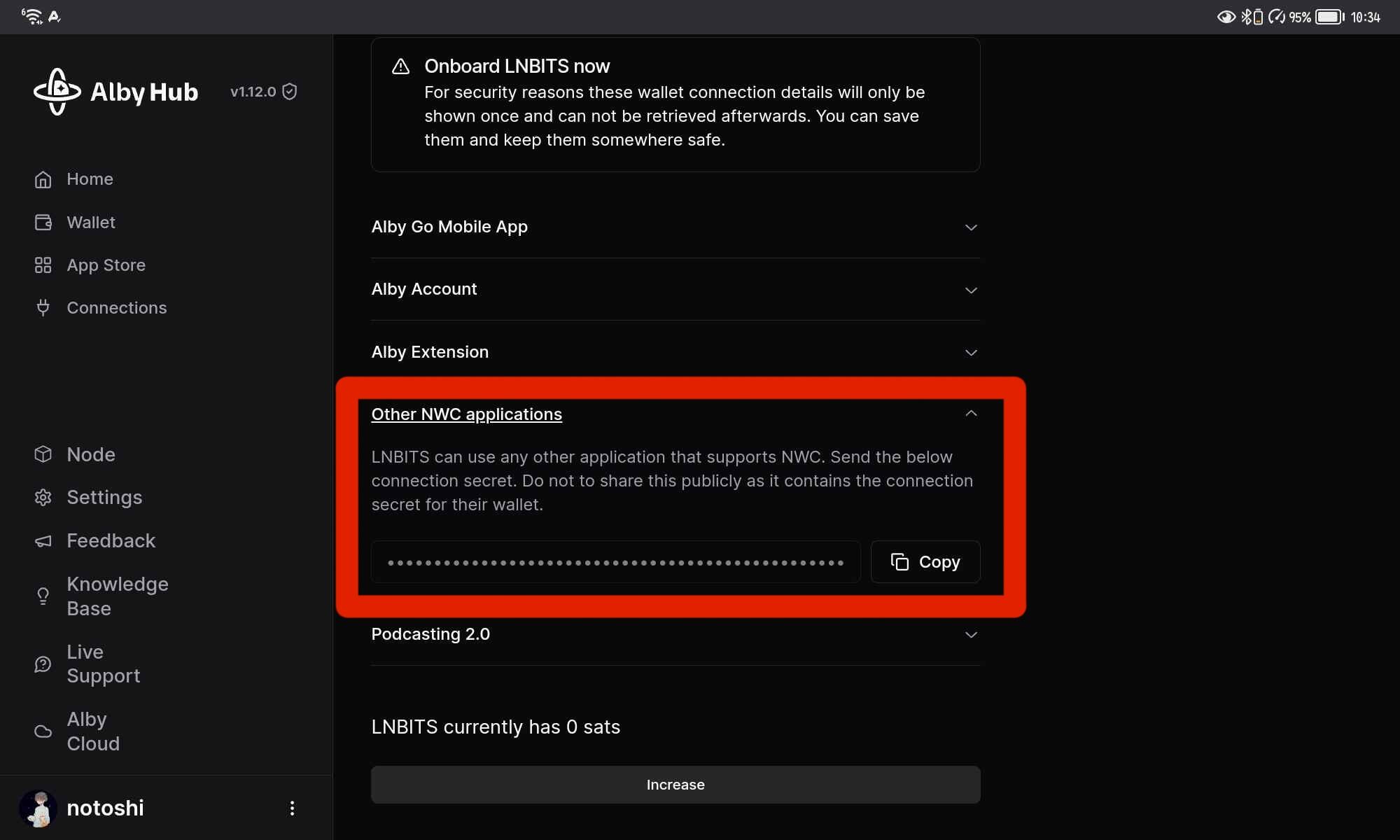
กลับมาที่ Lnbits วาง URL NWC
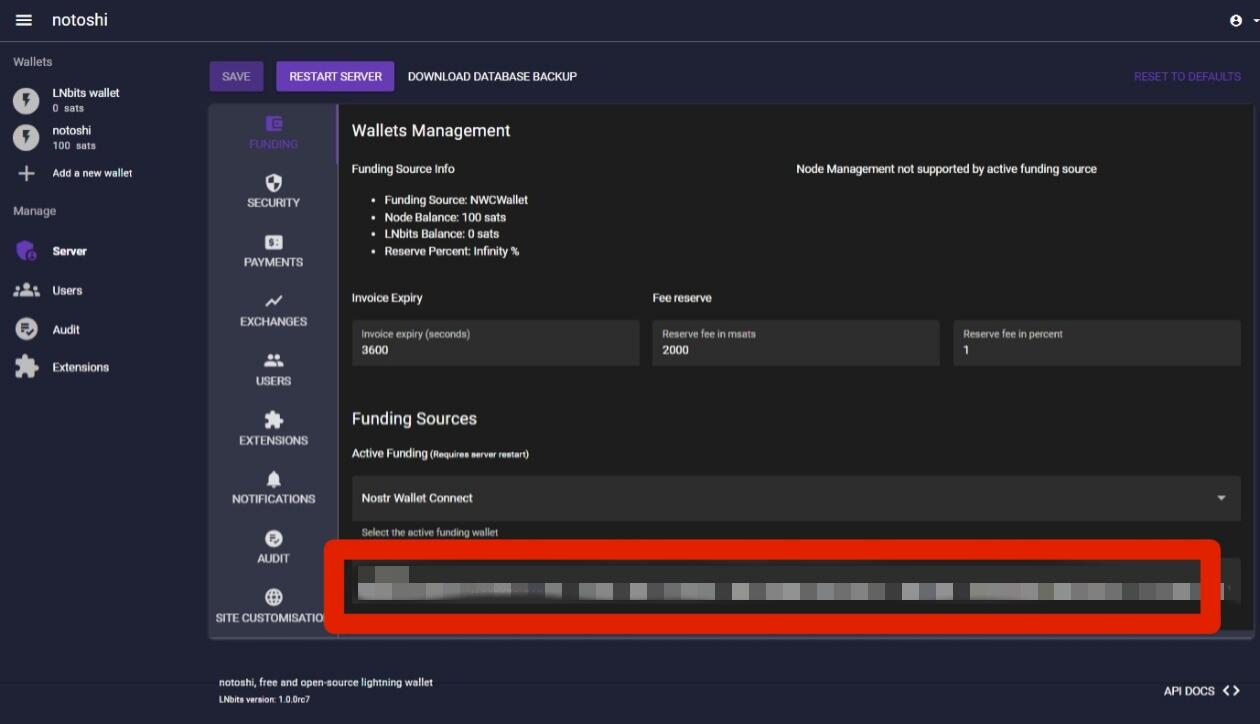
คลิก SAVE และ RESTART SERVER
แค่นี้ทุกอย่างพร้อมใช้งานแล้ว
อ่านข้อมูลเพิ่มเติมได้ที่ Lnbits: https://github.com/lnbits/lnbits Albyhub: https://github.com/getAlby/hub
หวังว่าบทความจะเป็นแนวทางในการติดตั้งที่ง่ายสำหรับทุกคนหากผิดพลาดประการใดคอมเม้นท์พูดคุยแนะนำได้ครับ
ขอบคุณทุกคนที่แวะมาอ่าน ไว้เจอกันไหม่
Siamstr
-
 @ f0c7506b:9ead75b8
2024-12-08 09:05:13
@ f0c7506b:9ead75b8
2024-12-08 09:05:13
Yalnızca güçlü olanların hakkıdır yaşamak.
Güçlü olan ileri gider ve saflar seyrekleşir. Ama üç beş büyük, güçlü ve tanrısal kişi güneşli ve aydınlık gözleriyle o yeni, o vaat edilmiş ülkeye ulaşacaktır. Belki binlerce yıl sonra ancak. Ve güçlü, adaleli, hükmetmek için yaratılmış elleriyle hastaların, zayıfların ve sakatların ölüleri üzerinde bir krallık kuracaklardır. Bir krallık!
Benim aradığım insanların kendileri değil, sesleridir.
Duyguları körelmiş, çeşitli düşüncelere saplanmış kalabalık hiçbir zaman ilerlemenin taşıyıcısı olamaz, kendi küçüklüğünün o küflü içgüdüsüyle kalabalığın kin ve nefretle baktığı bir kişi, bir büyük kişi, iradesinin gösterdiği yolda kimsenin gözünün yaşına bakmaksızın ilahi bir güç ve bir zafer gülümsemesiyle yürüyebilir ancak.
Bizim soyumuz da sonsuz oluşum piramidinin doruk noktasını oluşturmaktan uzaktır. Bizler de mükemmelliğe ulaşmış değiliz. Bizler de henüz olgunlaşmadık.
Şairler sevgiye övgüler döşenir; doğrusu sevginin güçlü bir şey olduğu kesin. Hüneşin bir ışınıdır sevgi, aydınlatıp nurlandırır insanı der bazıları; bazıları da insanı esrikliğe sürükleyen bir zehri kendisinde barındırdığını söyler. Gerçekten de yol açtığı sonuçlar, bir hekimin ağır bir ameliyattan önce korkudan titreyen hastaya teneffüs ettirdiği güldürücü gazınkine benzer, içinde tepinip duran acıyı unutturur hastaya.
Önemli olan, hayatta hiç değilse bir kez kutsal bir ilkbaharın yaşanmasıdır; öyle bir bahar ki, insanın gönlünü ilerideki bütün günleri altın yaldızla kaplamaya yetecek kadar ışık ve parıltıyla doldursun.
Şu hayat denen şey kötü bir işçiliğin ürünü, acemilere göre bir şey. Bu kepaze yaşam uğruna insan nelere katlanmıyor ki!
Kendisine sadakatten ayrılmadığı, yalnızca kendisinin olan bir tek bu var: Yalnızlığı.
Sahildeki üstü tenteli hasır koltuklar arkasındaki yüksek, sessiz kum tepeleri içinde yürürsen, tenteler altındaki insanları göremezsin; ama birinin bir diğerine seslendiğini, bir başkasının gevezelik ettiğini, bir ötekinin güldüğünü işitir ve anlarsın hemen: bu insan şöyle şöyle biridir diyebilirsin. Onun hayatı sevdiğini, bağrında büyük bir özlem ya da acı barındırdığını, bu acının da sesini ağlamaklı kıldığını her gülüşünde hissedersin.
-
 @ 65912a7a:5dc638bf
2024-12-08 05:33:02
@ 65912a7a:5dc638bf
2024-12-08 05:33:02Chef's notes
This is my late partner's award winning Cajun rice & beans recipe. It's an updated take on the traditional Cajun comfort food.
Chef Darin was a classically trained chef who spent 30+ years in the kitchen perfecting his recipes, and delivering authentic Cajun and Creole food to his patrons. This is a 5-star dish that will earn the respect of the most discerning Cajun afficionado. You won't be disappointed.
I suggest making this recipe exactly as directed the first time, and then make whatever adjustments you want for future batches. Also, don't cheap out on the Andouille. No Johnsonville or Hillshire Farms. Chef Aidelle's is a good choice, as is Silva's from Whole Foods. They cost a few extra bucks, but it's absolutely worth it.
Details
- ⏲️ Prep time: 30 min
- 🍳 Cook time: 3 hours
- 🍽️ Servings: 12
Ingredients
- 16oz small red beans, dry
- 2 cups long grain white rice
- 14-16oz andouille sausage, sliced
- 8oz ham, cubed
- 1 large yellow onion, chopped
- 1 green bell pepper, chopped
- 2-3 stalks celery, chopped
- 2 tbsp garlic (12 cloves), minced
- 7 cups water
- ¼ cup olive oil
- 2 large bay leaves
- 1 tbsp parsley, dried
- 1 tsp thyme, dried
- 1 tsp Cajun seasoning
- ½ tsp cayenne pepper, dried
- ¼ tsp sage, rubbed
- 1½ tsp salt (more or less to taste)
Directions
- Soak beans in a large pot of water overnight.
- Heat oil in a large stockpot over medium heat. Cook onion, bell pepper, celery, garlic in olive oil for 3 to 4 minutes (until onion is translucent).
- Add beans, bay leaves, parsley, thyme, salt, MSG, Cajun seasoning, cayenne pepper, Sage, and water. Stir, bring to a boil, and then reduce heat to medium-low (btwn 2-3). Cover and simmer for 2½ hours.
- Remove bay leaves. Mash some of the beans. Stir Andouille and ham into beans, and simmer uncovered for an additional 30 minutes.
- Meanwhile, prepare the rice. Bring water and rice to a boil in a saucepan. Reduce heat, cover, and simmer for 20 minutes.
- Serve beans over steamed white rice.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28O Planetinha
Fumaça verde me entrando pelas narinas e um coro desafinado fazia uma base melódica.
nos confins da galáxia havia um planetinha isolado. Era um planeta feliz.
O homem vestido de mago começava a aparecer por detrás da fumaça verde.
O planetinha recebeu três presentes, mas o seu habitante, o homem, estava num estado de confusão tão grande que ameaçava estragá-los. Os homens já havia escravizado o primeiro presente, a vida; lutavam contra o segundo presente, a morte; e havia alguns que achavam que deviam destruir totalmente o terceiro, o amor, e com isto levar a desordem total ao pobre planetinha perdido, que se chamava Terra.
O coro desafinado entrou antes do "Terra" cantando várias vezes, como se imitasse um eco, "terra-terra-terraaa". Depois de uma pausa dramática, o homem vestido de mago voltou a falar.
Terra, nossa nave mãe.
Neste momento eu me afastei. À frente do palco onde o mago e seu coral faziam apelos à multidão havia vários estandes cobertos com a tradicional armação de quatro pernas e lona branca. Em todos os cantos da praça havia gente, gente dos mais variados tipos. Visitantes curiosos que se aproximavam atraídos pela fumaça verde e as barraquinhas, gente que aproveitava o movimento para vender doces sem pagar imposto, casais que se abraçavam de pé para espantar o frio, os tradicionais corredores que faziam seu cooper, gente cheia de barba e vestida para imitar os hippies dos anos 60 e vender colares estendidos no chão, transeuntes novos e velhos, vestidos como baladeiros ou como ativistas do ônibus grátis, grupos de ciclistas entusiastas.
O mago fazia agora apelos para que nós, os homens, habitantes do isolado planetinha, passássemos a ver o planetinha, nossa nave mãe, como um todo, e adquiríssemos a consciência de que ele estava entrando em maus lençóis. A idéia, reforçada pela logomarca do evento, era que parássemos de olhar só para a nossa vida e pensássemos no planeta.
A logomarca do evento, um desenho estilizado do planeta Terra, nada tinha a ver com seu nome: "Festival Andando de Bem com a Vida", mas havia sido ali colocada estrategicamente pelos organizadores, de quem parecia justamente sair a mensagem dita pelo mago.
Aquela multidão de pessoas que, assim como eu, tinham suas próprias preocupações, não podiam ver o quadro caótico que formavam, cada uma com seus atos isolados, ali naquela praça isolada, naquele planeta isolado. Quando o hippie barbudo, quase um Osho, assustava um casal para tentar vender-lhes um colar, a quantidade de caos que isto acrescentava à cena era gigantesca. Por um segundo, pude ver, como se estivesse de longe e acima, com toda a pretensão que este estado imaginativo carrega, a cena completa do caos.
Uma nave-mãe, dessas de ficção científica, habitada por milhões de pessoas, seguia no espaço sem rumo, e sem saber que logo à frente um longo precipício espacial a esperava, para a desgraça completa sua e de seus habitantes.
Acostumados àquela nave tanto quanto outrora estiveram acostumados à sua terra natal, os homens viviam as próprias vidas sem nem se lembrar que estavam vagando pelo espaço. Ninguém sabia quem estava conduzindo a nave, e ninguém se importava.
No final do filme descobre-se que era a soma completa do caos que cada habitante produzia, com seus gestos egoístas e incapazes de levar em conta a totalidade, é que determinava a direção da nave-mãe. O efeito, no entanto, não era imediato, como nunca é. Havia gente de verdade encarregada de conduzir a nave, mas era uma gente bêbada, mau-caráter, que vivia brigando pelo controle da nave e o poder que isto lhes dava. Poder, status, dinheiro!
Essa gente bêbada era atraída até ali pela corrupção das instituições e da moral comum que, no fundo no fundo, era causada pelo egoísmo da população, através de um complexo -- mas que no filme aparece simplificado pela ação individual de um magnata do divertimento público -- processo social.
O homem vestido de mago era mais um agente causador de caos, com sua cena cheia de fumaça e sua roupa estroboscópica, ele achava que estava fazendo o bem ao alertar sua platéia, todos as sextas-feiras, de que havia algo que precisava ser feito, que cada um que estava ali ouvindo era responsável pelo planeta. A sua incapacidade, porém, de explicar o que precisava ser feito só aumentava a angústia geral; a culpa que ele jogava sobre seu público, e que era prontamente aceita e passada em frente, aos familiares e amigos de cada um, atormentava-os diariamente e os impedia de ter uma vida decente no trabalho e em casa. As famílias, estressadas, estavam constantemente brigando e os motivos mais insignificantes eram responsáveis pelas mais horrendas conseqüências.
O mago, que após o show tirava o chapéu entortado e ia tomar cerveja num boteco, era responsável por uma parcela considerável do caos que levava a nave na direção do seu desgraçado fim. No filme, porém, um dos transeuntes que de passagem ouviu um pedaço do discurso do mago despertou em si mesmo uma consiência transformadora e, com poderes sobre-humanos que lhe foram então concedidos por uma ordem iniciática do bem ou não, usando só os seus poderes humanos mesmo, o transeunte -- na primeira versão do filme um homem, na segunda uma mulher -- consegue consertar as instituições e retirar os bêbados da condução da máquina. A questão da moral pública é ignorada para abreviar a trama, já com duas horas e quarenta de duração, mas subentende-se que ela também fora resolvida.
No planeta Terra real, que não está indo em direção alguma, preso pela gravidade ao Sol, e onde as pessoas vivem a própria vida porque lhes é impossível viver a dos outros, não têm uma consciência global de nada porque só é possível mesmo ter a consciência delas mesmas, e onde a maioria, de uma maneira ou de outra, está tentando como pode, fazer as coisas direito, o filme é exibido.
Para a maioria dos espectadores, é um filme que evoca reflexões, um filme forte. Por um segundo elas têm o mesmo vislumbre do caos generalizado que eu tive ali naquela praça. Para uma pequena parcela dos espectadores -- entre eles alguns dos que estavam na platéia do mago, o próprio mago, o seguidor do Osho, o casal de duas mulheres e o vendedor de brigadeiros, mas aos quais se somam também críticos de televisão e jornal e gente que fala pelos cotovelos na internet -- o filme é um horror, o filme é uma vulgarização de um problema real e sério, o filme apela para a figura do herói salvador e passa uma mensagem totalmente errada, de que a maioria da população pode continuar vivendo as suas própria vidinhas miseráveis enquanto espera por um herói que vem do Olimpo e os salva da mixórdia que eles mesmos causaram, é um filme que presta um enorme desserviço à causa.
No dia seguinte ao lançamento, num bar meio caro ali perto da praça, numa mesa com oito pessoas, entre elas seis do primeiro grupo e oito do segundo, discute-se se o filme levará ou não o Oscar. Eu estou em casa dormindo e não escuto nada.
-
 @ 3bf0c63f:aefa459d
2024-12-06 20:37:26
@ 3bf0c63f:aefa459d
2024-12-06 20:37:26início
"Vocês vêem? Vêem a história? Vêem alguma coisa? Me parece que estou tentando lhes contar um sonho -- fazendo uma tentativa inútil, porque nenhum relato de sonho pode transmitir a sensação de sonho, aquela mistura de absurdo, surpresa e espanto numa excitação de revolta tentando se impôr, aquela noção de ser tomado pelo incompreensível que é da própria essência dos sonhos..."
Ele ficou em silêncio por alguns instantes.
"... Não, é impossível; é impossível transmitir a sensação viva de qualquer época determinada de nossa existência -- aquela que constitui a sua verdade, o seu significado, a sua essência sutil e contundente. É impossível. Vivemos, como sonhamos -- sozinhos..."
- Livros mencionados por Olavo de Carvalho
- Antiga homepage Olavo de Carvalho
- Bitcoin explicado de um jeito correto e inteligível
- Reclamações
-
 @ f977c464:32fcbe00
2024-01-11 18:47:47
@ f977c464:32fcbe00
2024-01-11 18:47:47Kendisini aynada ilk defa gördüğü o gün, diğerleri gibi olduğunu anlamıştı. Oysaki her insan biricik olmalıydı. Sözgelimi sinirlendiğinde bir kaşı diğerinden birkaç milimetre daha az çatılabilirdi veya sevindiğinde dudağı ona has bir açıyla dalgalanabilirdi. Hatta bunların hiçbiri mümkün değilse, en azından, gözlerinin içinde sadece onun sahip olabileceği bir ışık parlayabilirdi. Çok sıradan, öyle sıradan ki kimsenin fark etmediği o milyonlarca minik şeyden herhangi biri. Ne olursa.
Ama yansımasına bakarken bunların hiçbirini bulamadı ve diğer günlerden hiç de farklı başlamamış o gün, işe gitmek için vagonunun gelmesini beklediği alelade bir metro istasyonunda, içinde kaybolduğu illüzyon dağılmaya başladı.
İlk önce derisi döküldü. Tam olarak dökülmedi aslında, daha çok kıvılcımlara dönüşüp bedeninden fırlamış ve bir an sonra sönerek külleşmiş, havada dağılmıştı. Ardında da, kaybolmadan hemen önce, kısa süre için hayal meyal görülebilen, bir ruhun yok oluşuna ağıt yakan rengârenk peri cesetleri bırakmıştı. Beklenenin aksine, havaya toz kokusu yayıldı.
Dehşete düştü elbette. Dehşete düştüler. Panikle üstlerini yırtan 50 işçi. Her şeyin sebebiyse o vagon.
Saçları da döküldü. Her tel, yere varmadan önce, her santimde ikiye ayrıla ayrıla yok oldu.
Bütün yüzeylerin mat olduğu, hiçbir şeyin yansımadığı, suyun siyah aktığı ve kendine ancak kameralarla bakabildiğin bir dünyada, vagonun içine yerleştirilmiş bir aynadan ilk defa kendini görmek.
Gözlerinin akları buharlaşıp havada dağıldı, mercekleri boşalan yeri doldurmak için eriyip yayıldı. Gerçeği görmemek için yaratılmış, bu yüzden görmeye hazır olmayan ve hiç olmayacak gözler.
Her şeyin o anda sona erdiğini sanabilirdi insan. Derin bir karanlık ve ölüm. Görmenin görmek olduğu o anın bitişi.
Ben geldiğimde ölmüşlerdi.
Yani bozulmuşlardı demek istiyorum.
Belleklerini yeni taşıyıcılara takmam mümkün olmadı. Fiziksel olarak kusursuz durumdaydılar, olmayanları da tamir edebilirdim ama tüm o hengamede kendilerini baştan programlamış ve girdilerini modifiye etmişlerdi.
Belleklerden birini masanın üzerinden ileriye savurdu. Hınca hınç dolu bir barda oturuyorlardı. O ve arkadaşı.
Sırf şu kendisini insan sanan androidler travma geçirip delirmesin diye neler yapıyoruz, insanın aklı almıyor.
Eliyle arkasını işaret etti.
Polislerin söylediğine göre biri vagonun içerisine ayna yerleştirmiş. Bu zavallılar da kapı açılıp bir anda yansımalarını görünce kafayı kırmışlar.
Arkadaşı bunların ona ne hissettirdiğini sordu. Yani o kadar bozuk, insan olduğunu sanan androidi kendilerini parçalamış olarak yerde görmek onu sarsmamış mıydı?
Hayır, sonuçta belirli bir amaç için yaratılmış şeyler onlar. Kaliteli bir bilgisayarım bozulduğunda üzülürüm çünkü parasını ben vermişimdir. Bunlarsa devletin. Bana ne ki?
Arkadaşı anlayışla kafasını sallayıp suyundan bir yudum aldı. Kravatını biraz gevşetti.
Bira istemediğinden emin misin?
İstemediğini söyledi. Sahi, neden deliriyordu bu androidler?
Basit. Onların yapay zekâlarını kodlarken bir şeyler yazıyorlar. Yazılımcılar. Biliyorsun, ben donanımdayım. Bunlar da kendilerini insan sanıyorlar. Tiplerine bak.
Sesini alçalttı.
Arabalarda kaza testi yapılan mankenlere benziyor hepsi. Ağızları burunları bile yok ama şu geldiğimizden beri sakalını düzeltip duruyor mesela. Hayır, hepsi de diğerleri onun sakalı varmış sanıyor, o manyak bir şey.
Arkadaşı bunun delirmeleriyle bağlantısını çözemediğini söyledi. O da normal sesiyle konuşmaya devam etti.
Anlasana, aynayı falan ayırt edemiyor mercekleri. Lönk diye kendilerini görüyorlar. Böyle, olduğu gibi...
Nedenmiş peki? Ne gerek varmış?
Ne bileyim be abicim! Ahiret soruları gibi.
Birasına bakarak dalıp gitti. Sonra masaya abanarak arkadaşına iyice yaklaştı. Bulanık, bir tünelin ucundaki biri gibi, şekli şemalı belirsiz bir adam.
Ben seni nereden tanıyorum ki ulan? Kimsin sen?
Belleği makineden çıkardılar. İki kişiydiler. Soruşturmadan sorumlu memurlar.
─ Baştan mı başlıyoruz, diye sordu belleği elinde tutan ilk memur.
─ Bir kere daha deneyelim ama bu sefer direkt aynayı sorarak başla, diye cevapladı ikinci memur.
─ Bence de. Yeterince düzgün çalışıyor.
Simülasyon yüklenirken, ayakta, biraz arkada duran ve alnını kaşıyan ikinci memur sormaktan kendisini alamadı:
─ Bu androidleri niye böyle bir olay yerine göndermişler ki? Belli tost olacakları. İsraf. Gidip biz baksak aynayı kırıp delilleri mahvetmek zorunda da kalmazlar.
Diğer memur sandalyesinde hafifçe dönecek oldu, o sırada soruyu bilgisayarın hoparlöründen teknisyen cevapladı.
Hangi işimizde bir yamukluk yok ki be abi.
Ama bir son değildi. Üstlerindeki tüm illüzyon dağıldığında ve çıplak, cinsiyetsiz, birbirinin aynı bedenleriyle kaldıklarında sıra dünyaya gelmişti.
Yere düştüler. Elleri -bütün bedeni gibi siyah turmalinden, boğumları çelikten- yere değdiği anda, metronun zemini dağıldı.
Yerdeki karolar öncesinde beyazdı ve çok parlaktı. Tepelerindeki floresan, ışığını olduğu gibi yansıtıyor, tek bir lekenin olmadığı ve tek bir tozun uçmadığı istasyonu aydınlatıyorlardı.
Duvarlara duyurular asılmıştı. Örneğin, yarın akşam kültür merkezinde 20.00’da başlayacak bir tekno blues festivalinin cıvıl cıvıl afişi vardı. Onun yanında daha geniş, sarı puntolu harflerle yazılmış, yatay siyah kesiklerle çerçevesi çizilmiş, bir platformdan düşen çöp adamın bulunduğu “Dikkat! Sarı bandı geçmeyin!” uyarısı. Biraz ilerisinde günlük resmi gazete, onun ilerisinde bir aksiyon filminin ve başka bir romantik komedi filminin afişleri, yapılacakların ve yapılmayacakların söylendiği küçük puntolu çeşitli duyurular... Duvar uzayıp giden bir panoydu. On, on beş metrede bir tekrarlanıyordu.
Tüm istasyonun eni yüz metre kadar. Genişliği on metre civarı.
Önlerinde, açık kapısından o mendebur aynanın gözüktüğü vagon duruyordu. Metro, istasyona sığmayacak kadar uzundu. Bir kılıcın keskinliğiyle uzanıyor ama yer yer vagonların ek yerleriyle bölünüyordu.
Hiçbir vagonda pencere olmadığı için metronun içi, içlerindekiler meçhuldü.
Sonrasında karolar zerrelerine ayrılarak yükseldi. Floresanın ışığında her yeri toza boğdular ve ortalığı gri bir sisin altına gömdüler. Çok kısa bir an. Afişleri dalgalandırmadılar. Dalgalandırmaya vakitleri olmadı. Yerlerinden söküp aldılar en fazla. Işık birkaç kere sönüp yanarak direndi. Son kez söndüğünde bir daha geri gelmedi.
Yine de etraf aydınlıktı. Kırmızı, her yere eşit dağılan soluk bir ışıkla.
Yer tamamen tele dönüşmüştü. Altında çapraz hatlarla desteklenmiş demir bir iskelet. Işık birkaç metreden daha fazla aşağıya uzanamıyordu. Sonsuzluğa giden bir uçurum.
Duvarın yerini aynı teller ve demir iskelet almıştı. Arkasında, birbirine vidalarla tutturulmuş demir plakalardan oluşan, üstünden geçen boruların ek yerlerinden bazen ince buharların çıktığı ve bir süre asılı kaldıktan sonra ağır, yağlı bir havayla sürüklendiği bir koridor.
Diğer tarafta paslanmış, pencerelerindeki camlar kırıldığı için demir plakalarla kapatılmış külüstür bir metro. Kapının karşısındaki aynadan her şey olduğu gibi yansıyordu.
Bir konteynırın içini andıran bir evde, gerçi gayet de birbirine eklenmiş konteynırlardan oluşan bir şehirde “andıran” demek doğru olmayacağı için düpedüz bir konteynırın içinde, masaya mum görüntüsü vermek için koyulmuş, yarı katı yağ atıklarından şekillendirilmiş kütleleri yakmayı deniyordu. Kafasında hayvan kıllarından yapılmış grili siyahlı bir peruk. Aynı kıllardan kendisine gür bir bıyık da yapmıştı.
Üstünde mavi çöp poşetlerinden yapılmış, kravatlı, şık bir takım.
Masanın ayakları yerine oradan buradan çıkmış parçalar konulmuştu: bir arabanın şaft mili, üst üste konulmuş ve üstünde yazı okunamayan tenekeler, boş kitaplar, boş gazete balyaları... Hiçbir şeye yazı yazılmıyordu, gerek yoktu da zaten çünkü merkez veri bankası onları fark ettirmeden, merceklerden giren veriyi sentezleyerek insanlar için dolduruyordu. Yani, androidler için. Farklı şekilde isimlendirmek bir fark yaratacaksa.
Onların mercekleri için değil. Bağlantıları çok önceden kopmuştu.
─ Hayatım, sofra hazır, diye bağırdı yatak odasındaki karısına.
Sofrada tabak yerine düz, bardak yerine bükülmüş, çatal ve bıçak yerine sivriltilmiş plakalar.
Karısı salonun kapısında durakladı ve ancak kulaklarına kadar uzanan, kocasınınkine benzeyen, cansız, ölü hayvanların kıllarından ibaret peruğunu eliyle düzeltti. Dudağını, daha doğrusu dudağının olması gereken yeri koyu kırmızı bir yağ tabakasıyla renklendirmeyi denemişti. Biraz da yanaklarına sürmüştü.
─ Nasıl olmuş, diye sordu.
Sesi tek düzeydi ama hafif bir neşe olduğunu hissettiğinize yemin edebilirdiniz.
Üzerinde, çöp poşetlerinin içini yazısız gazete kağıtlarıyla doldurarak yaptığı iki parça giysi.
─ Çok güzelsin, diyerek kravatını düzeltti kocası.
─ Sen de öylesin, sevgilim.
Yaklaşıp kocasını öptü. Kocası da onu. Sonra nazikçe elinden tutarak, sandalyesini geriye çekerek oturmasına yardım etti.
Sofrada yemek niyetine hiçbir şey yoktu. Gerek de yoktu zaten.
Konteynırın kapısı gürültüyle tekmelenip içeri iki memur girene kadar birbirlerine öyküler anlattılar. O gün neler yaptıklarını. İşten erken çıkıp yemyeşil çimenlerde gezdiklerini, uçurtma uçurduklarını, kadının nasıl o elbiseyi bulmak için saatlerce gezip yorulduğunu, kocasının kısa süreliğine işe dönüp nasıl başarılı bir hamleyle yaşanan krizi çözdüğünü ve kadının yanına döndükten sonra, alışveriş merkezinde oturdukları yeni dondurmacının dondurmalarının ne kadar lezzetli olduğunu, boğazlarının ağrımasından korktuklarını...
Akşam film izleyebilirlerdi, televizyonda -boş ve mat bir plaka- güzel bir film oynayacaktı.
İki memur. Çıplak bedenleriyle birbirinin aynı. Ellerindeki silahları onlara doğrultmuşlardı. Mum ışığında, tertemiz bir örtünün serili olduğu masada, bardaklarında şaraplarla oturan ve henüz sofranın ortasındaki hindiye dokunmamış çifti gördüklerinde bocaladılar.
Hiç de androidlere bilinçli olarak zarar verebilecek gibi gözükmüyorlardı.
─ Sessiz kalma hakkına sahipsiniz, diye bağırdı içeri giren ikinci memur. Söylediğiniz her şey...
Cümlesini bitiremedi. Yatak odasındaki, masanın üzerinden gördüğü o şey, onunla aynı hareketleri yapan android, yoksa, bir aynadaki yansıması mıydı?
Bütün illüzyon o anda dağılmaya başladı.
Not: Bu öykü ilk olarak 2020 yılında Esrarengiz Hikâyeler'de yayımlanmıştır.
-
 @ 3ffac3a6:2d656657
2024-12-22 02:16:45
@ 3ffac3a6:2d656657
2024-12-22 02:16:45In a small, quiet town nestled between rolling hills, there lived a boy named Ravi. Ravi was resourceful, hardworking, and had a knack for finding ways to support his family. His mother, a widow who worked tirelessly as a seamstress, inspired Ravi to pitch in wherever he could. His latest venture was ironing clothes for neighbors.
With his trusty old iron and a rickety wooden table, Ravi turned a small corner of their modest home into a makeshift laundry service. By day, he attended school and played with his friends, but in the evenings, he transformed into the “Iron Boy,” smoothing out wrinkles and earning a few precious coins.
One night, orders piled up after a local wedding had left everyone with wrinkled formalwear. Determined to finish, Ravi worked well past his usual bedtime. The warm glow of the lamp cast long shadows across the room as he focused on the rhythmic hiss of steam escaping the iron.
Just as the clock struck midnight, a soft clop-clop echoed from outside. Ravi froze, the iron hovering mid-air. The sound grew louder until it stopped right outside his window.
A deep, resonant voice broke the silence. “Didn’t your mother tell you not to be ironing clothes late at night?”
Ravi’s heart jumped into his throat. He turned slowly to the window, and his eyes widened. Standing there, framed by the moonlight, was a horse—a magnificent creature with a shimmering coat and a mane that seemed to ripple like liquid silver. Its dark eyes sparkled with an otherworldly light, and its lips moved as it spoke.
“W-who are you?” Ravi stammered, clutching the iron like a shield.
The horse tilted its head. “Names are not important. But you should know that ironing past midnight stirs things best left undisturbed.”
“Things? What things?” Ravi asked, his curiosity momentarily overriding his fear.
The horse snorted softly, a sound that almost resembled a chuckle. “Spirits. Shadows. Call them what you will. They grow restless in the heat of the iron at night. You don’t want to invite them in.”
Ravi glanced at the clothes piled on the table, then back at the horse. “But I need to finish these. People are counting on me.”
The horse’s eyes softened, and it stepped closer to the window. “Your dedication is admirable, but heed my warning. For tonight, let it be. Finish in the morning.”
Before Ravi could reply, the horse reared slightly, its silver mane glinting in the moonlight. With a final, cryptic look, it trotted off into the darkness, leaving Ravi staring after it in stunned silence.
The next morning, Ravi woke to find his mother standing at the table, finishing the last of the ironing. “You were so tired, I thought I’d help,” she said with a smile.
Ravi hesitated, then decided not to mention the midnight visitor. But from that day on, he made sure to finish his ironing before nightfall.
Though he never saw the horse again, he sometimes heard the faint clop-clop of hooves in the distance, as if reminding him of that strange, magical night. And in his heart, he carried the lesson that some tasks are best left for the light of day.
-
 @ 148755e6:450c107f
2024-12-05 10:09:32
@ 148755e6:450c107f
2024-12-05 10:09:32突然荒野に行きたくなったので行ってきたエントリーです
まずは練習。高尾山へ
Nostrは古今東西ありとあらゆるオフ会が生えており、
まるで荒野に行きたいという私の意志を完全に汲み取ったかのように「紅葉を見にいこうようオフ」がそこに生えていたので参加した。(しおんさんご主催ありがとうございました)
前半1時間くらいの坂道がマジきつかったです。前半キツすぎて後半足痛かった。。 終始人がいっぱいいて渋谷かと思った。
確かに道がかなり整備されていて、逆にコンクリート故に足が疲れたのかもしれない。隣の人は途中の急な坂道で足を滑らせてて、横で転倒事故が起きるかと思いました。
山頂に行っても人がたくさんいて、迷子になりかけた。あそこはスクランブル交差点や。 そして山頂の先にあるもみじ台まで歩くと人がまばらで、まったりして蕎麦食べたりしながら休憩して下山。
登りは暑くて汗かきましたが、山頂でまったりしてると汗も引いてきて少し冷えました。
下山はスイスイ。16時近くで結構暗かったので、冬の間は早めの登頂・下山がおすすめですね。
登り2時間・下り1時間半で概ね見込み通りって感じでした。
高尾山は登ってると景色が変わります。ちょっと開けた場所に出て下の街が見えたり、草木があったり、階段があったり、参道があったり。。そういう意味では退屈しない2時間でした。
ビギナー山とはいえ、革靴やヒールのある靴で登ってる人がいてびっくり。ツルッと滑ることあると思いますので、スニーカーで登ることをお勧めします。
舐めプしてたとはいえめちゃくちゃキツかったおもひで。
更なる練習。小浅間山へ
さて私は荒野に行きたいワケなのですが、高尾山に荒野はありませんでした。更なる練習として小浅間山へ。
前日(か前々日)に雪が降ったようで、山に雪が残っておりました。
それでも都内の汚れてべちゃっとした感じの雪ではなく、粉砂糖がちょっと積もってるみたいな感じで綺麗だった。
登り前半の30分くらい、景色や道が変わらず、ずっと歩きっぱなしになってしまいました。時間みて休憩しながら行けばよかったなあ。
登るにつれて気温が下がっていくのか、積雪が厚くなっていく。
40分くらいは割と平坦な道が続きますが、突然山頂っぽいものが現れて、「これを登れっていうのかい...?」とビビるほどピーンと急な道が出てきました。(写真だと分かりづらいですね)
ただ、高尾山のコンクリート道に比べると足の疲れはそこまででした。雪道なので気をつけて歩くという意味では疲れましたが、春〜秋とかは快適に登れるんじゃないでしょうか。
山頂に到着するとドーンと浅間山が見えて圧巻。
風が強くて飛ばされる恐怖はありましたが、なんとか無事でいられました。あったかいお茶美味しかった〜。
なぜかギャルの看板があって、謎でした。写真はひとまずありません。
山頂が2箇所あって、それぞれで眺めを満喫していたら結構時間が経ってました。
小さい背丈くらいの木や足元にちょっとした植物があったり、自分的にはかなり理想の荒野に近かったです。(植物に対する解像度が低すぎる) 往復で2時間程度の山らしいんですが、なんやかんやと2時間半強くらいいた気がします。
荒野ビギナーは小浅間山に往け
というわけで、荒野に行きたい人はまずは小浅間山を登ると良いと思います。 また登りたい。
荒野部部長
一緒に高尾山・小浅間山に登ってくれた方、ありがとうございました! 個人的には来年の春までに秩父多摩甲斐国立公園に行き、来年の秋までに大山隠岐国立公園に行くという目標を立ててるんですが、 少々時間が空くので次どこに行こうかしらと考えているところです。
ヒントとしては、火山で、あまり高低差のないところだとビギナーの私にちょうど良さそうです。
とある情報筋によると伊豆大島が良さそうなので、次の機会に行けたらと思っています。
みんなで荒野に行こう!
-
 @ 7776c32d:45558888
2024-12-21 23:45:13
@ 7776c32d:45558888
2024-12-21 23:45:13I am still more censored than I was when Aaron Swartz was alive. For nostr to resist censorship, it would need a way for intellectuals to find each other and not be drowned out by anti-intellectual screeching.
Nostr is currently so anti-intellectual that this propagandist gets multiple likes, probably enough to be in trending feeds, for a post (she's reposted herself) pretending the word "car" is the best example she can think of for media bias today.
Meanwhile, I get no engagement for bringing a valuable infographic about media bias over from X.
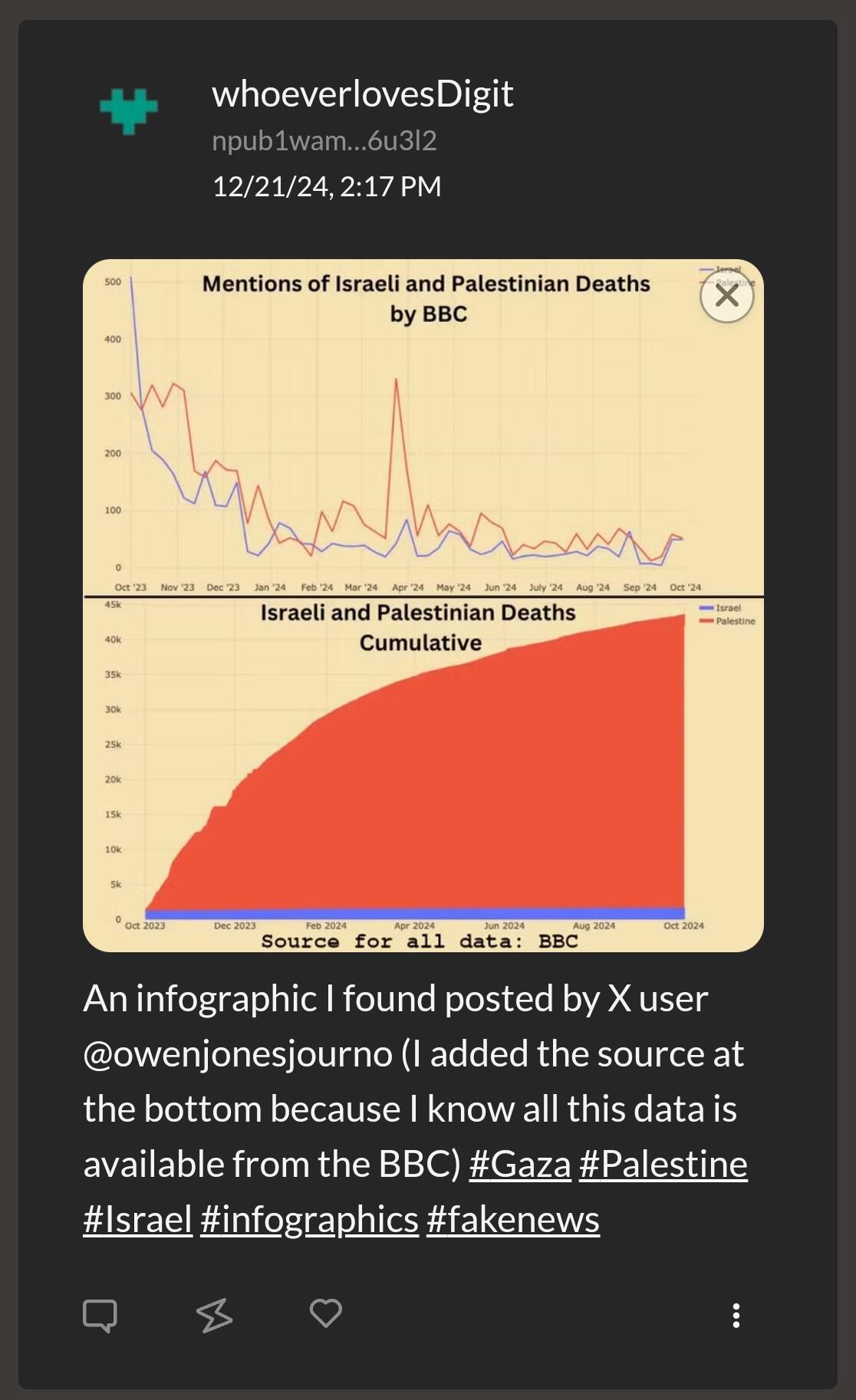
The same incoherent propagandist gets multiple likes on a post lying about Hawk Tuah token. She doesn't quote post my prior post about the same topic to give credit to me as a faster news reporter, because she knows I am not a fake news reporter, meaning I will correct her misinformation, and indeed my post already contradicts some of it (the part about Haliey herself being sued).
Notice the lack of likes on my replies calling out her misinformation; and also none on my earlier, more accurate post about the same topic. The dishonest propaganda gets all the likes while the actual reporting on the same topic, faster, gets none.
When I've called out this retard's lies on the same topic in the past, getting almost no engagement has been the norm, but it's been negative engagement overall.
Here's her and some reply guy gaslighting me and, as always, she did not follow up to actually address my points, apologize, or hold any attempt at genuine, good-faith discussion in general.
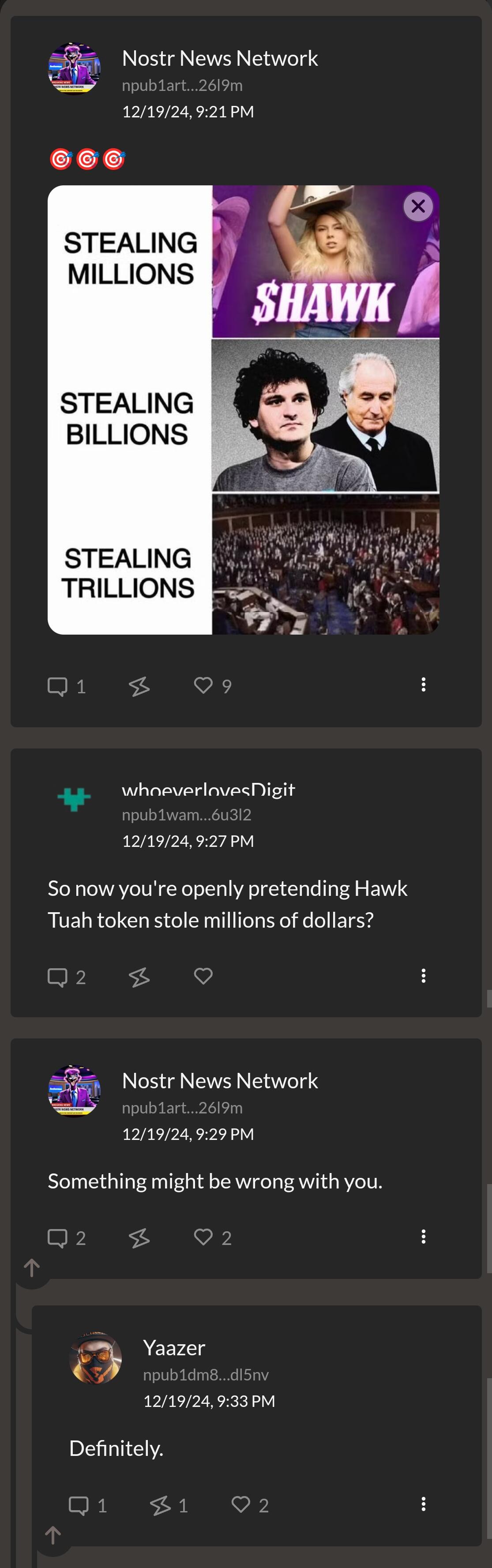
It's not like I'm cherry picking. Let's look at the statistics.
According to nostr.band this anti-intellectual dickhead has reposted 33 events (from 8 other npubs), and her posts have been reposted 666 times. I have reposted 367 events (from 214 other npubs), and mine have been reposted 108 times.
But enough about her.
The #pandemic hashtag has gone from being full of pandemic deniers to having more people talking about the next pandemic - bird flu - while still nobody on that hashtag is using nostr to talk about COVID, the ongoing pandemic we still have.
nostr:nevent1qqs9gvuhvphwvxm96zl58ygxdp3w8jjpyl2hqhg0j2xhxfms73qls8sw7yhx3
I have stood for well over a year as the only person in the group of English speakers smart enough to understand the importance of both the pandemic and decentralized digital networks. That's so fucking depressing, enraging, and terrifying to me.
This shit makes me bloodthirsty. Luckily I can get away with killing people sometimes; and more often, inconveniencing them, by stealing essential parts from the boxes of products they'll buy, or cutting them off in traffic, or other things like that, to vent my disdain for my fellow humans.
People lie so much, the main comfort for me has been the brief time when Digit considered me a friend; she who seemed to also kinda see through all the lies.
You know what's stopping me from hurting anyone right now? The hope that Digit is still alive, and I keep thinking about this thread, where she was mentioned.
Someone showed curiosity about her, and someone else said "thank you (and Digit) so much." That "thank you and Digit" has been keeping me going on less toxic energy for those few days.
-
 @ 32e18276:5c68e245
2023-12-06 15:29:43
@ 32e18276:5c68e245
2023-12-06 15:29:43I’m going to be on an ordinals panels as one of the people who is counter arguing the claim that they are good for bitcoin. I decided to brush up on the technicals on how inscriptions work. I am starting to see luke’s perspective on how it is exploiting a loophole in bitcoin’s anti-data-spam mechanisms.
Storing data in Bitcoin, the “standard” way
The standard way you add “data” to bitcoin is by calling the OP_RETURN opcode. Bitcoin devs noticed that people were storing data (like the bitcoin whitepaper) in the utxo set via large multisig transactions. The problem with this is that this set is unprunable and could grow over time. OP_RETURN outputs on the other-hand are provably prunable and don’t add to utxo bloat.
Here’s an excerpt from the march 2014 0.9.0 release notes that talks about this:
On OP_RETURN: There was been some confusion and misunderstanding in the community, regarding the OP_RETURN feature in 0.9 and data in the blockchain. This change is not an endorsement of storing data in the blockchain. The OP_RETURN change creates a provably-prunable output, to avoid data storage schemes – some of which were already deployed – that were storing arbitrary data such as images as forever-unspendable TX outputs, bloating bitcoin’s UTXO database. Storing arbitrary data in the blockchain is still a bad idea; it is less costly and far more efficient to store non-currency data elsewhere.
Much of the work on bitcoin core has been focused on making sure the system continues to function in a decentralized way for its intended purpose in the presence of people trying to abuse it for things like storing data. Bitcoin core has always discouraged this, as it is not designed for storage of images and data, it is meant for moving digital coins around in cyberspace.
To help incentive-align people to not do stupid things, OP_RETURN transactions were not made non-standard, so that they are relayable by peers and miners, but with the caveat:
- They can only push 40 bytes (later increased to 80,83, I’m guessing to support larger root merkle hashes since that is the only sane usecase for op_return)
Bitcoin also added an option called -datacarriersize which limits the total number of bytes from these outputs that you will relay or mine.
Why inscriptions are technically an exploit
Inscriptions get around the datacarriersize limit by disguising data as bitcoin script program data via OP_PUSH inside OP_IF blocks. Ordinals do not use OP_RETURN and are not subjected to datacarriersize limits, so noderunners and miners currently have limited control over the total size of this data that they wish to relay and include in blocks. Luke’s fork of bitcoin-core has some options to fight this spam, so hopefully we will see this in core sometime soon as well.
Inscriptions are also taking advantage of features in segwit v1 (witness discount) and v2/taproot (no arbitrary script size limit). Each of these features have interesting and well-justified reasons why they were introduced.
The purpose of the witness discount was to make it cheaper to spend many outputs which helps the reduction of the utxo set size. Inscriptions took advantage of this discount to store monke jpegs disguised as bitcoin scripts. Remember, bitcoin is not for storing data, so anytime bitcoin-devs accidentally make it cheap and easy to relay data then this should be viewed as an exploit. Expect it to be fixed, or at least provide tools to noderunners for fighting this spam.
Where do we go from here
The interesting part of this story is that people seem to attach value to images stored on the bitcoin blockchain, and they are willing to pay the fee to get it in the block, so non-ideologic miners and people who don’t care about the health and decentralization of bitcoin are happy to pay or collect the fee and move on.
Data should not get a discount, people should pay full price if they want to store data. They should just use op_return and hashes like opentimestamps or any other reasonable protocol storing data in bitcoin.
After going through this analysis I’ve come to the opinion that this is a pretty bad data-spam exploit and bitcoin devs should be working on solutions. Ideological devs like luke who actually care about the health and decentralization of the network are and I’m glad to see it.
-
 @ 5fb7f8f7:d7d76024
2024-12-19 07:29:19
@ 5fb7f8f7:d7d76024
2024-12-19 07:29:19As Bitcoin keeps breaking new height it's important to also keep track of Altcoins movement too. Stay positioned this bullrun season and make money $. Carry out research on tokens, coins and even memecoin to buy and stay positioned for next year. I'll be suggesting a few you can buy and hold to get maximum profit.
BGB: bitget exchange native token CORE: integrated BTC into its staking programm BLUEFIN: last ATH was at $10 currently $0.6 SUI: hitting $8 soon position yourself DOGS: under TON ecosystem TON: native token of Ton Blockchain NOTCOIN: The first memecoin on Ton Blockchain AVACN: good token to hold for bullrun SPUNKYSDX: I bought at $10 currently at $26 and many more research and find out. I'll be dropping more so follow like and comment so you don't miss out.
money #finance #BTC #Altcoins
-
 @ fcb65172:87f3c4ed
2024-12-21 21:59:04
@ fcb65172:87f3c4ed
2024-12-21 21:59:04Cities on return are often strange\ Yeah, and now\ Every time you blink, you feel it change\ And it's been\ A long, a long, a long, a long, long-long\ You've been my\ Favourite for a while
So sings Grian Chatten, lead singer of the Irish punk band Fontaines D.C (look them up and thank me later), in the fourth verse of their song Favourite– my favourite track released in 2024. As a world traveller who has called quite a few places home during the past 10 years I can relate to these lyrics on so many levels.
It just so happens that I recently came back to La Paz, Bolivia– a city I used to call home. But so many things about the city has changed. Most notably with old friends of mine.
Some old friends have turned out to reveal themselves as crooks, and you guessed it, some of the people who had been painted, in my mind, as crooks– well it just so turns out that they have revealed themselves as the good guys. I’m reminded of Warren Buffet’s line: Only when the tide goes out do you discover who's been swimming naked. The time away from La Paz has given me time to reflect on my two and a half years living here. The time component acts as the tide in Buffet’s great quote– Allowing me to filter through all the noise and focus on what is real. Or should I say who of my old friends were the real friends and who were the crooks– swimming naked all the time.
My Story with La Paz
I first arrived in La Paz in 2018 as a 22 year old boy looking for a place in South America to live. La Paz was where I met my wife. La Paz is where I bought my first business– a pub in the tourist area. La Paz is where I learned to deal with corrupt city council workers. La Paz is in many ways where I grew from a boy to a man.
 A Young 22 Year old naive version of me in La Paz
A Young 22 Year old naive version of me in La PazFast forward to December 2024 as I’m back in the city for the first time in two years. Walking the colourful and chaotic streets of La Paz, brings back all the memories. The street corner where a young naive Sebastian bought his first gram of pure Bolivian Marching Powder– That shit will pick you right up by the bootstraps, but do to proceed with care, I don’t have enough available fingers to count the amount of people who I’ve seen lose their lives to the Marching Powder of Bolivia. If you aren’t careful it will become the only thing you live for.
I jump on a cable car– La Paz’s metro system which flies across the city, up and down the mountains, connecting all neighbourhoods with the city centre. I head to what used to be my local park and viewpoint. This is where I would always come to read a book or listen to podcasts whilst enjoying the stunning view of Illimani– the mountain guarding La Paz. Most importantly this is the park where I made my first move to kiss my wife.
 The view of Illimani Mountain from the Pub I used to own
The view of Illimani Mountain from the Pub I used to ownThe former community leader who vanished
The main thing I think about as I re-explore my old neighbourhoods is; what happened to my old friends and acquaintances? Together with the other restaurants in the tourist area we used to have a football team organised by a true community leader, let’s call him George in this story, the team was called Chocos Locos– The Crazy Blondes, we were a mix of European expats, exchanges students, NGO employees and some local Bolivian friends of ours. George was the guy who tied us all together. He knew everyone– their birthday, what football team they supported, what drink they preferred etc. George would look out for everyone, he would make sure to organize birthday parties, even for the quiet ones in our group. George had his values set in the right place, he demanded a high standard from everyone on and off the pitch. In exchange we would look out for each other, cover for one another if we were in trouble. You know like the Marines, we would leave no man behind.
As I’m now back in La Paz most of my former friends and teammates are no longer around, George included. Their restaurants are closed and new ones have emerged. Some have left due to the recent years of political instability in Bolivia, others have mysteriously disappeared. What happened to them?
In May 2024 I received a message from George saying our friend and teammate, let’s call him Juan, was in intensive care in a hospital in La Paz, after suffering a near death accident. Juan’s family needed help to cover the treatment costs. Like the true community leader George is, he took it upon himself to reach out to all present and former teammates and friends of Juan, asking us all to pitch in, with whatever we could to support Juan’s treatment. I didn’t think much else of it and sent across €100 to support Juan. As I later came to learn, the story was something else. The real story revealed George’s true identity.
This is the story of a real captain, a true community leader, who turned out to be a scammer. But how did George turn into a scammer who used the near death accident of a friend and teammate, to scam just about everyone who had ever met Juan into donating money to help Juan’s family pay for the intensive care in hospital, only to run off with all the money donated– approximately $4000 USD?
Perhaps the answer was there in front of our faces all along? I recently listened to a podcast with Andrew Bustamente (a former CIA spy, known as Everyday Spy on YouTube) in the podcast Andrew mentioned that most people who come off as highly empathetic, people like George, aren’t actually as highly empathetic as they seem, in fact such people despise almost everybody else.
I now ask myself did George actually use the community and our football team the whole time. Were we funding his life in La Paz all the time? George told us he was working online as an English teacher. Now I ask myself who George really was.
See you all in 2025
It’s mind blowing to me, how time removed from a former favourite city helps us see our time living in said city with such clarity… What really happened? Who were the good guys? Who were the bad guys?
As I look to settle into a new hometown in 2025 (more on that in future newsletters) I will keep in mind my lessons learned from revisiting La Paz. I will be able to spot who are the charlatan’s and who are the genuine good guys– or at least so I hope.
As I warm up to a Holiday season with family from both Denmark and Bolivia I wish you all a great Holidays, remember to be grateful for your family and those who are your real friends. Show them love. Cherish your time with them. Let me leave you with the lyrics to the final verse of the fantastic Fontaines D.C song Favourite:
Ah, makes sense when you understand\ The misery made me another marked man\ And I'm always looking over my shoulder\ And each new day\ - I get another year older\ Shoulder bound to the frame of a door\ Tuned into shape like a stone on the shore\ But if there was lightning in me\ Then you know who it was for
https://www.youtube.com/watch?v=1UG31mpUnOg
I will see you all in 2025. God bless you all.
Sebastian
-
 @ 8fb140b4:f948000c
2023-11-21 21:37:48
@ 8fb140b4:f948000c
2023-11-21 21:37:48Embarking on the journey of operating your own Lightning node on the Bitcoin Layer 2 network is more than just a tech-savvy endeavor; it's a step into a realm of financial autonomy and cutting-edge innovation. By running a node, you become a vital part of a revolutionary movement that's reshaping how we think about money and digital transactions. This role not only offers a unique perspective on blockchain technology but also places you at the heart of a community dedicated to decentralization and network resilience. Beyond the technicalities, it's about embracing a new era of digital finance, where you contribute directly to the network's security, efficiency, and growth, all while gaining personal satisfaction and potentially lucrative rewards.
In essence, running your own Lightning node is a powerful way to engage with the forefront of blockchain technology, assert financial independence, and contribute to a more decentralized and efficient Bitcoin network. It's an adventure that offers both personal and communal benefits, from gaining in-depth tech knowledge to earning a place in the evolving landscape of cryptocurrency.
Running your own Lightning node for the Bitcoin Layer 2 network can be an empowering and beneficial endeavor. Here are 10 reasons why you might consider taking on this task:
-
Direct Contribution to Decentralization: Operating a node is a direct action towards decentralizing the Bitcoin network, crucial for its security and resistance to control or censorship by any single entity.
-
Financial Autonomy: Owning a node gives you complete control over your financial transactions on the network, free from reliance on third-party services, which can be subject to fees, restrictions, or outages.
-
Advanced Network Participation: As a node operator, you're not just a passive participant but an active player in shaping the network, influencing its efficiency and scalability through direct involvement.
-
Potential for Higher Revenue: With strategic management and optimal channel funding, your node can become a preferred route for transactions, potentially increasing the routing fees you can earn.
-
Cutting-Edge Technological Engagement: Running a node puts you at the forefront of blockchain and bitcoin technology, offering insights into future developments and innovations.
-
Strengthened Network Security: Each new node adds to the robustness of the Bitcoin network, making it more resilient against attacks and failures, thus contributing to the overall security of the ecosystem.
-
Personalized Fee Structures: You have the flexibility to set your own fee policies, which can balance earning potential with the service you provide to the network.
-
Empowerment Through Knowledge: The process of setting up and managing a node provides deep learning opportunities, empowering you with knowledge that can be applied in various areas of blockchain and fintech.
-
Boosting Transaction Capacity: By running a node, you help to increase the overall capacity of the Lightning Network, enabling more transactions to be processed quickly and at lower costs.
-
Community Leadership and Reputation: As an active node operator, you gain recognition within the Bitcoin community, which can lead to collaborative opportunities and a position of thought leadership in the space.
These reasons demonstrate the impactful and transformative nature of running a Lightning node, appealing to those who are deeply invested in the principles of bitcoin and wish to actively shape its future. Jump aboard, and embrace the journey toward full independence. 🐶🐾🫡🚀🚀🚀
-
-
 @ ac8bb9b0:70278acc
2024-12-04 20:30:30
@ ac8bb9b0:70278acc
2024-12-04 20:30:30Chef's notes
Make Ahead: You can prepare this recipe up to one week in advance. Store it in an airtight container in the refrigerator.
To Freeze: Allow the dish to cool completely before transferring it to a freezer-safe bag. Lay the bag flat in the freezer to ensure even freezing and to save space. Thaw it in the refrigerator overnight before using it.
Details
- ⏲️ Prep time: 5
- 🍳 Cook time: 5
- 🍽️ Servings: 1
Ingredients
- ½ cup soy sauce
- 2 Tablespoons rice vinegar
- 1 Tablespoon sesame oil
- 1/4 cup + 1 Tablespoon light brown sugar
- 1 Tablespoon honey
- 3/4 teaspoon ground ginger
- 1 clove garlic , minced
- 2 teaspoons cornstarch+ 2 tsp water , mixed together to make a cornstarch slurry
- 1/4 teaspoon crushed red pepper flakes
Directions
- Make the teriyaki sauce by adding all of the sauce ingredients to a small saucepan over medium heat.
- Bring to a boil, stirring constantly, and boil for about 1 minute. The sauce should be thick enough to coat the back of the spoon.
- Serve over rice or with a stir-fry. See post above for additional ideas.
-
 @ 31e3a4de:ae1b209d
2024-12-21 21:09:43
@ 31e3a4de:ae1b209d
2024-12-21 21:09:43Here’s a thought experiment: What if healthcare insurance is fundamentally the wrong model for managing most healthcare? Insurance works best when it covers the unexpected—the tail-risk events that hit you out of nowhere. But the reality is that much of healthcare isn’t unexpected at all.
Take cancer as an example. The initial diagnosis and treatment are undeniably shocking—a classic insurance-worthy moment. But what about the next five or ten years of follow-up care? That’s not surprising. It’s predictable. Should insurance, a system designed for surprises, really foot the bill for something so foreseeable?
Here’s the argument: health insurance should cover the initial shock—like a cancer diagnosis or a torn hamstring during a sports match. But once the acute phase passes, predictable, long-term care (like cancer surveillance or diabetes management) should be handled differently—perhaps through government funding.
Consider chronic illnesses. If someone with poorly controlled diabetes develops retinal disease or vascular complications, is that surprising? Not really. It’s almost inevitable. Asking insurers to cover these predictable outcomes results in inflated premiums and financial inefficiency.
The same logic applies to other chronic conditions. A smoker with diabetes developing vascular disease? It’s not a question of “if” but “when.” Why pretend this is an insurable risk?
Here’s the punchline: if we separate the unexpected from the inevitable in healthcare, we might just create a more efficient system. Insurance should handle the surprises. Government funding should manage the predictable. And the sooner we recognize that most of healthcare isn’t a surprise, the sooner we can build a system that works for everyone.
Here’s a thought experiment: What if healthcare insurance is fundamentally the wrong model for managing most healthcare? Insurance works best when it covers the unexpected—the tail-risk events that hit you out of nowhere. But the reality is that much of healthcare isn’t unexpected at all.
Take cancer as an example. The initial diagnosis and treatment are undeniably shocking—a classic insurance-worthy moment. But what about the next five or ten years of follow-up care? That’s not surprising. It’s predictable. Should insurance, a system designed for surprises, really foot the bill for something so foreseeable?
Here’s the argument: health insurance should cover the initial shock—like a cancer diagnosis or a torn hamstring during a sports match. But once the acute phase passes, predictable, long-term care (like cancer surveillance or diabetes management) should be handled differently—perhaps through government funding.
Consider chronic illnesses. If someone with poorly controlled diabetes develops retinal disease or vascular complications, is that surprising? Not really. It’s almost inevitable. Asking insurers to cover these predictable outcomes results in inflated premiums and financial inefficiency.
The same logic applies to other chronic conditions. A smoker with diabetes developing vascular disease? It’s not a question of “if” but “when.” Why pretend this is an insurable risk?
Here’s the punchline: if we separate the unexpected from the inevitable in healthcare, we might just create a more efficient system. Insurance should handle the surprises. Government funding should manage the predictable. And the sooner we recognize that most of healthcare isn’t a surprise, the sooner we can build a system that works for everyone.
-
 @ de496884:72617b81
2023-11-20 13:54:02
@ de496884:72617b81
2023-11-20 13:54:02Hola nostriches. Hoy quiero hacer una publicación a modo de acercamiento al surgimiento de las categorías de género y feminismo. Así que si te interesa el tema haz un esfuerzo, quédate y lee hasta el final.
El «nuevo» feminismo surge en los años 60 en aquellos países desarrollados que acordaron el reconocimiento a los derechos humanos contenidos en la declaración respectiva de la ONU. Entonces, como extensión a dicho reconocimiento es que se gesta el movimiento feminista. A partir de entonces, se vuelve a plantear la relación entre naturaleza y cultura y se llega a la conclusión de que las diferencias sociales van más allá de las diferencias biológicas, lo cual tiene que ver con que hasta la satisfacción de las necesidades elementales como son la alimentación, la vivienda o el vestuario, están condicionadas por construcciones sociales.
Pues resulta que una de las primeras propuestas identificó la subordinación femenina producto de una organización patriarcal, tomando la categoría patriarcado de Max Weber. Es así como la visión de patriarcado se extendió al discurso político y académico. Sin embargo, no existía información acerca del desarrollo histórico de dicha categoría, sistematización, variaciones, etc., debido a que era algo que recién se percibía en sociedad.
Sin embargo, la misma categoría de patriarcado junto a la de relaciones de poder para explicar fenómenos sociales contemporáneos, constituye uno de los principales aportes del feminismo. Es así como han logrado primero visibilizar y luego deconstruir y desmontar una serie de patrones existentes en la cultura que hacían a la mujer subordinarse al hombre, y que estaban presentes en el sistema sexo/género.
 Imagen relativa a la lucha contra el patriarcado
Imagen relativa a la lucha contra el patriarcadoHasta ese momento, en las investigaciones de corte sociológico se podía observar un androcentrismo excesivo al dar cuenta de que el discurso científico giraba en torno al hombre como sujeto y objeto de la investigación. Incluso para muchos positivistas como el mismo Weber, los problemas relativos a las mujeres quedaban en un segundo plano y eran achacados a una supuesta pasividad en el ámbito doméstico-familiar. Dicha pasividad partía de la supuesta inferioridad biológica del género femenino.
El patriarcado entonces era una categoría vacía en sí misma, sin valor explicativo. Desde el punto de vista político pudo ser útil para la movilización pero no resistió la polémica de los críticos del feminismo ni problematizó los conflictos a ser resueltos. Pero por otro lado, un grupo de mujeres -académicas principalmente- se puso manos a la obra en una tarea más pequeña pero con mayores resultados a la larga. Se propusieron generar conocimientos sobre las condiciones de vida de la mujer, buscar en el pasado y el presente los aportes de las mujeres a la sociedad, hacerlas visibles en la historia. Es así como surgen centros académicos, ONG, proyectos, centros de estudios sobre la mujer, etc.
Convendría distinguir entonces dos posturas que acompañaron a la investigación sobre las mujeres: uno que toma como objeto de estudio a la mujer; condiciones de vida, trabajo, cultura, y otra que privilegia a la sociedad como generadora de la subordinación de las mujeres. Mientras la primera perspectiva generaba conocimiento sobre las mujeres en el estudio de las relaciones mujer-hombre y mujer-mujer, la segunda tenía una visión más holística ya que planteaba que hay que estudiar la sociedad ya que la subordinación de las mujeres es producto de la organización de esta, y que no se avanzará solamente estudiando a las mujeres, pues el estudio debe ser más amplio y en diferentes niveles, ámbitos y tiempos.
Es en esta búsqueda donde nace y se desarrolla el concepto de género como categoría social. Es así que los sistemas de género/sexo fueron entendidos como conjuntos de prácticas, símbolos, representaciones, normas y valores sociales que las sociedades construyen a partir de la diferencia anatomofisiológica y que dotan de sentido a los impulsos sexuales, la reproducción y en general a las relaciones de las personas. Por tanto, este sistema pasó a ser el objeto de estudio para comprender la subordinación de la mujer al hombre. Al ser el reconocimiento de una dimensión de la desigualdad social hasta entonces desconocida, se considera la ruptura epistemológica más importante de la segunda mitad del siglo pasado.
 Imagen representativa del binarismo de género
Imagen representativa del binarismo de géneroHay que decir que los fenómenos sociales se definen por la relación que guardan entre sí. Es así que la contextualización adquiere gran importancia. Varones y hembras tenemos la capacidad de producir con el cuerpo, pero solo los cuerpos de las hembras pueden gestar y por tanto asegurar la especie humana. Todo grupo humano que pretenda sobrevivir debe asegurarse cierto número de hembras que lo hagan posible. De ahí un poder particular del cuerpo de las hembras que además es económicamente útil. Dicho poder no es en tanto entidad biológica, sino que es la sociedad la que le otorga este poder. En este punto es importante preguntarnos históricamente ¿quiénes han controlado la capacidad reproductiva de las mujeres?, ¿quiénes han tenido la preferencia en el acceso sexual? Para asegurar un control efectivo sobre la reproducción es necesario asegurar el acceso a la sexualidad.
Ello también lleva a dirigir el trabajo que hacen porque de lo contrario, las mujeres pudieran tener espacio para representar una amenaza al dominio de los hombres. Es importante atender a las etapas del desarrollo de las mujeres, que permitirá ver cómo se moldean para aceptar la desigualdad y las jerarquías según el género en las distintas sociedades y culturas.
Otro contexto a delimitar es el ámbito doméstico donde históricamente ha estado ubicada la subordinación femenina. Se ha puesto al descubierto que en mujeres que comparten la misma posición de clase y raza, la condición femenina se redefine a lo largo de la vida y que algunas mujeres gozan de poder sobre otras aún en contextos de alta dominación masculina, donde se les inviste de autoridad, creando el sistema zonas de incertidumbre que las divide como género e impide alianzas y se legitima la dominación. Foucault decía que «el poder se ejerce, no se posee», siempre está en peligro de perderse y no basta con normas, leyes, amenazas o castigos. De ahí que los espacios de subordinación sean también espacios de poder de las mujeres. Es en estos espacios donde aparece la inseguridad, la tensión, la confrontación y por ejemplo, las mujeres pueden reclamar la anticoncepción.
Para terminar, es importante tener en cuenta que el género es una forma de desigualdad social que siempre está articulado con otras formas de desigualdad ya sea clase, raza, grupo etario, etc. Hay que pensar la dominación masculina con un comienzo vago en el tiempo, pero que permite desligar la subordinación de las mujeres de la evolución «natural» de la humanidad y entenderla como un proceso histórico. En ese sentido es necesario destacar que, respecto a la raza, en sociedades plurales hay que atender al contexto étnico-cultural ya que en dependencia de las relaciones entre personas de razas distintas, estarán condicionadas las relaciones entre los géneros.
 Imagen de mujeres de distintas razas
Imagen de mujeres de distintas razasPor otro lado, si bien es sabido que históricamente el sistema de género social imperante ha contribuido a invisibilizar a la mujer, asociar necesariamente dicha categoría únicamente a ella, lo que hace es nuevamente recrear el absolutismo histórico que tanto daño ha hecho, ahora como lo antagónico al hombre. En la construcción social participan todos los individuos presentes en el sistema género.
Hasta aquí la publicación de hoy, de la cual aun se puede ahondar mucho más, sobre todo en lo referido al origen de la dominación o de la jerarquización del binomio «hombre/mujer» desde un punto de vista antropológico, pero eso quedará pendiente para otro momento. ¡Así que hasta la próxima!, ¡nos vemos en Nostr!
........................................
English version
Hello nostriches. Today I want to make a post by way of an approach to the emergence of the categories of gender and feminism. So if you are interested in the topic make an effort, stay and read to the end.
The "new" feminism emerged in the 60's in those developed countries that agreed to recognize the human rights contained in the respective UN declaration. Then, as an extension of that recognition, the feminist movement was born. From then on, the relationship between nature and culture was raised again and the conclusion was reached that social differences go beyond biological differences, which has to do with the fact that even the satisfaction of elementary needs such as food, housing or clothing are conditioned by social constructions.
It turns out that one of the first proposals identified female subordination as a product of a patriarchal organization, taking Max Weber's category of patriarchy. This is how the vision of patriarchy was extended to political and academic discourse. However, there was no information about the historical development of this category, systematization, variations, etc., because it was something that was only recently perceived in society.
However, the same category of patriarchy, together with that of power relations to explain contemporary social phenomena, constitutes one of the main contributions of feminism. This is how they have first made visible and then deconstructed and dismantled a series of existing patterns in the culture that made women subordinate to men, and that were present in the sex/gender system.
 Image relating to the fight against patriarchy
Image relating to the fight against patriarchyUp to that time, in sociological research, an excessive androcentrism could be observed as scientific discourse revolved around men as the subject and object of research. Even for many positivists such as Weber himself, the problems related to women remained in the background and were blamed on a supposed passivity in the domestic-family sphere. This passivity was based on the supposed biological inferiority of the female gender.
Patriarchy was then an empty category in itself, with no explanatory value. From the political point of view, it could be useful for mobilization, but it did not resist the polemic of feminism's critics, nor did it problematize the conflicts to be resolved. But on the other hand, a group of women - mainly academics - set to work on a smaller task but with greater results in the long run. They set out to generate knowledge about women's living conditions, to search in the past and present for women's contributions to society, to make them visible in history. This is how academic centers, NGOs, projects, women's studies centers, etc., came into being.
It would be convenient to distinguish then two postures that accompanied the research on women: one that takes women as the object of study; living conditions, work, culture, and the other that privileges society as the generator of women's subordination. While the first perspective generated knowledge about women in the study of woman-man and woman-woman relations, the second had a more holistic vision, since it proposed that society must be studied, since the subordination of women is a product of its organization, and that progress will not be made only by studying women, since the study must be broader and at different levels, spheres and times.
It is in this search that the concept of gender as a social category was born and developed. Thus, gender/sex systems were understood as a set of practices, symbols, representations, norms and social values that societies construct on the basis of anatomophysiological differences and that give meaning to sexual impulses, reproduction and, in general, to people's relationships. Therefore, this system became the object of study to understand the subordination of women to men. As the recognition of a hitherto unknown dimension of social inequality, it is considered the most important epistemological breakthrough of the second half of the last century.
 Representative image of gender binarism
Representative image of gender binarismIt must be said that social phenomena are defined by their relationship with each other. Thus, contextualization acquires great importance. Males and females have the capacity to produce with their bodies, but only the bodies of females can gestate and therefore ensure the human species. Any human group that intends to survive must ensure a certain number of females to make it possible. Hence a particular power of the female body, which is also economically useful. This power is not as a biological entity, but it is society that gives it this power. At this point it is important to ask ourselves historically, who has controlled the reproductive capacity of women, who has had the preference in sexual access? To ensure effective control over reproduction, it is necessary to ensure access to sexuality.
 Allegorical image of pregnancy
Allegorical image of pregnancyThis also leads to directing the work they do because otherwise, women may have room to pose a threat to men's dominance. It is important to pay attention to the stages of women's development, which will allow us to see how they are shaped to accept inequality and gender hierarchies in different societies and cultures.
Another context to delimit is the domestic sphere where female subordination has historically been located. It has been discovered that in women who share the same class and race position, the feminine condition is redefined throughout life and that some women enjoy power over others even in contexts of high male domination, where they are invested with authority, creating the system of uncertainty zones that divide them as a gender and prevent alliances and legitimize domination. Foucault said that "power is exercised, not possessed", it is always in danger of being lost and norms, laws, threats or punishments are not enough. Hence, the spaces of subordination are also spaces of women's power. It is in these spaces where insecurity, tension, confrontation appear and where, for example, women can demand contraception.
To conclude, it is important to keep in mind that gender is a form of social inequality that is always articulated with other forms of inequality, be it class, race, age group, etc. It is necessary to think of male domination with a vague beginning in time, but which allows us to separate the subordination of women from the "natural" evolution of humanity and to understand it as a historical process. In this sense, it is necessary to emphasize that, with respect to race, in plural societies it is necessary to pay attention to the ethno-cultural context since, depending on the relations between people of different races, the relations between genders will be conditioned.
 Image of women of different races
Image of women of different racesOn the other hand, although it is known that historically the prevailing social gender system has contributed to make women invisible, to necessarily associate this category only to women is to recreate the historical absolutism that has done so much damage, this time as antagonistic to men. All individuals present in the gender system participate in the social construction.
So much for today's publication, of which we can still go much deeper, especially with regard to the origin of domination or the hierarchization of the binomial "man/woman" from an anthropological point of view, but that will be left for another time. So until next time, see you in Nostr!
Créditos | Credits
Bibliografía consultada | Consulted bibliography:
-
Barbieri, T. (1993). Sobre la categoría género. Una introducción teórico-metodológica. Debates en Sociología. (18). 1-19. https://doi.org/10.18800/debatesensociologia.199301.006
-
Echevarría, D. (2020). Desigualdades de género e interseccionalidad. Análisis del contexto cubano 2008-2018. Facultad Latinoamericana de Ciencias Sociales (Programa-Cuba). https://www.clacso.org.ar/libreria-latinoamericana-cm/libro_detalle_resultado.php?id_libro=2346&campo=cm&texto=248
Traducción | Translation:
DeepL
-
-
 @ 26bb2ebe:70530958
2024-12-02 16:46:10
@ 26bb2ebe:70530958
2024-12-02 16:46:10nostterに画像最適化機能つけたよ(サーバー編)
この記事はNostr Advent Calendar 2024 の3日目の記事です。
あまり技術的な話はないので暇つぶし程度に読んでみてください。
どうしてこうなった?
そもそも認証の改善以前にNostrあんまり人が増えてないのが一番課題だよねと思ったのが始まりでした。 Nostrに人が増えないのはオーガニック検索流入が少ないからに違いないと特に根拠もなく思ったのでNostrのまとめサイト(Toggeter)のようなものを作ろうと考えました。
ところでNostrのまとめを行うアプリ自体は鎌倉さんという方がノスリというのを作成されていました。ブログ形式のイベントにTwitterライクな短文投稿をまとめるというものでまさしくToggeterですが、そこまで活用されていません。 そこでその仕組みをありがたくそのまま転用してまとめ記事を何らかの方法で量産しつつ、一つのドメインのサイトにまとめてSEOもなんかうまいことやれば検索流入増えるんじゃねという目論みです。
ところでそのまとめサイトは静的サイトジェネレータで(SSG:Static Site Generator)でつくりたいなと思いました。いや普通に考えてSSRにしてサーバ側でNostrからデータとってきたらSEO的にもよくねって感じなんですが、SSRでサーバーでウェブソケット呼ぶのだる…レイテンシを考慮すると結構不利じゃないかなと思ったわけです。うそです。そこまで考えてなくてほとんど個人的な好みです。(多分ちゃんとキャッシュきかせればそんなにレイテンシ問題にならなさそうな気がする)。ただキャッシュとかも考慮すると結構複雑な気はする。
ということで今年の6月頃にNostrのブログ記事をSSGするサイトをためしに作りました。 去年のアドベントカレンダー記事とか乗っけてます。
全然画像最適化の話になりませんね。もうちょっとです。
SSGのブログといえばGatsby(今は下火かも)とかで作成した経験があります。Gatsbyでは画像用のプラグインが公式に用意されていて生成されたブログに表示される画像はもとの画像データから変換され、表示時のサイズに最適化されたサイズにリサイズすることができます。
それだけではなくサイトの初期表示時には画像の画質を落としてぼやけた画像を表示してその後元画像が読み込まれたらきれいな画像を表示する、みたいなことができます。インラインでデータを持っているのでHTMLの表示と同時に画像の初期表示ができたりします。(その頃はよくわかってなかったがNostrのNIP-92で定義されているblurhashとかを使っていたんでしょう多分)
とにかくSSGは初期表示の速さが良い。というのが自分の頭の中にあるわけです。SSGのブログをNostrで作るとなると当然同じことがやりたい。
しかし、Nostrの画像はただのURLです。(オプショナルで画像のメタデータを定義できるimetaタグはあるが…)
基本的にSSGの画像最適化というのはローカルに存在する画像データをビルド時に変換するという流れで行われます。もしくはリモートURLに画像が置かれる場合は画像ストレージサービスやCDN上で配信されるときに最適化されることになります。
Nostrの画像はただの外部のURLですから(2回目)、ローカルの画像を変換する方法は採用できないわけです。無理やり実行するならビルド時にURLからすべての画像を一旦ダウンロードして変換するとかも考えましたが、ただの外部URLというのはつまりは一体どういうファイルなのかダウンロードしてみるまでわからない、要するに全然信頼できないということですから、よくわからないURLをかたっぱしからダウンロードするようなことは避けたいわけですね。(極端な話100GBの画像URLとかつくって攻撃されたら破綻しますよね)
ここが結構他の中央集権的なSNSと違って辛いところなのかなと思います。X(Twitter)とかであれば画像ストレージサーバは一つなので表示される画像の形式も一つに限定されるのですが、画像のアップロードが外部頼みでただのURLなので(3回目)何が来るかわからないということですね。
サーバ側で画像形式などを制限できない(imetaも信頼できるかわからない)となるとクライアント側でなんとか対応する必要があり、Nostrはクライアント側が大変なプロトコルだなあとということに思いを馳せていましたが、いろいろ考えたり調べた結果として作るべきものは画像最適化のためのプロキシサーバであるということがわかりました。
プロキシサーバというのはここでどういう働きをするのかというと、もとの画像がおいてあるサーバとクライアントのあいだに入って、もとの画像を一旦ダウンロードして圧縮したり縮小したりしてそのあとクライアントに送ってあげるという働きをします。
プロキシがないとき
[画像置き場] -> [クライアント]プロキシがあるとき
[画像置き場] -> [プロキシ] -> [クライアント]利点としてはクライアントが実際にダウンロードするのはサイズの小さな画像になるので通信量や画像の表示スピードは改善します。が、一方でサーバを経由する分通信にかかる時間(レイテンシ)が長くなります。というわけなので、当初の目的である表示速度の改善を実現するには、画像をエッジキャッシュするなどの対応が必須となります。平たく言うと一度送った画像はプロキシで保存しておいて次に要求されたらそれをすぐ返すということです。
画像をどれくらいのサイズにするか、画質はどうするかなどはプロキシに指示してあげれば良いのでクライアント側は想定通りの画像を受け取れてハッピーということになります。嘘です。ある程度はハッピーですが、プロキシ自体がエラーを返す可能性もあるし、処理できなくてもとの画像をそのまま返す場合もあります。そんなあれこれの結果、クライアントはフォールバック処理を実装する必要がありました。(それはまた別の記事で)
一方で自分はNostrのモバイルクライアントのヘビーユーザですので、Nostrの通信量の多さも解決したい課題でした。Nostrやってるとすぐギガがなくなります。 通信量の多さのボトルネックはウェブソケットで送られるNostrのイベントの通信量というよりは投稿に添付される画像のダウンロードの方ではないかという話もTLで耳にしたため(特に裏もとらず)、いっちょ画像最適化のプロキシサーバを作ってクライアントに実装してプルリクエスト投げるかと考えました。
そこで私はまずクライアントをAmethystからnostterに乗り換えることから始めました。なぜならばAmethystよりもTypeScriptとSvelteで書かれているnostterのほうがコントリビュートしやすかったという私的な事情です。
解決したい課題
遠回りしてきましたが課題はこれ。
- Nostrの画像の表示改善
- Nostrの通信量の改善
インターフェイス(設計)
画像最適化のプロキシは実装よりもインターフェースを考えるのが大変です。ここはとても苦労しそうな気がしたので、何も考えず cloudflare Imagesのインターフェースをそのまま借用することにしました。
https://developers.cloudflare.com/images/transform-images/transform-via-url/
また何かあってもcloudflare Imageに課金して乗り換えることが可能という利点もあります。
実装
とにかく時間がないので手グセでかけるTypeScriptかJS。かつ課金しないで可用性を維持できる無料枠のサーバレス環境が使いたかったので cloudflare workers に目星をつけて調査したところ、非常に素晴らしい記事を見つけましたのでこのwasmのライブラリをTSから呼び出して使わせていただくことにしました。
自分の実装したところはURLのパースと、キャッシュAPIの呼び出しを行って、最後にこのライブラリを叩くだけです。 ほかはクライアントキャッシュ用のヘッダーを書き換えたりとか細かいことはやっていますが全く大したことはやっておらず、サーバは非常にリーズナブルにやりたいことを実装した形になりました。 大変助かりました。
実装したものがこちらです。
https://github.com/ocknamo/nostr-image-optimizer
実装後の課題
このプロキシただのパブリックAPIなのでDoS攻撃に弱いです。何回もAPIをたたかれたら無料枠をすぐに超えてしまうことが容易に想像できました。 無料枠超えても使えなくなるだけで破産はしないので安心ですが、しかし対策は考える必要があります。
WAF
WAFです。APIに対するリクエスト回数などに対する制限をIPごとにかけています。また攻撃された場合検知できれば特定のIPや地域をブラックリストに入れることも可能です。
細かいことを説明してギリギリを攻めて攻撃されても困るので細かく説明しませんが、当初は全力でDoS攻撃されても無料枠超えないくらいの感じで制限をかけていました。 しかしNostrのTLをちょっと早めに表示するとすぐにWAFに引っかかってエラーになるという状態になることもあり、結局アイコンの表示は画像最適化の対象にしない方針にするなどの影響がありました。
いろいろあって、前提が変わり、もう少し制限をゆるくしたのでアイコンの対応は今後は検討できるかもしれません。
まとめ
割と手抜きで作ったことがわかるかと思います。実装しててNostrへの貢献ではあるはずですが、Nostrのプロトコル(NIPsとか)全然関係ないことやってるなと思いました。
フロントについては来週書きます。
次回のアドベントカレンダーの記事は eyemono.moe さんによる”クライアント自作を通して得られた知見まとめ”ですね!楽しみです!
-
 @ c48e29f0:26e14c11
2024-12-17 16:33:04
@ c48e29f0:26e14c11
2024-12-17 16:33:04titcoin
Rename Bitcoin to "Titcoin" and sats to "tits."
Redefinition of Bitcoin into “Titcoin” and redefinition of sats into “tits” using that as the Unit Base of Denomination.
TitHub repository available here: https://github.com/WalkerAmerica/titcoin
Abstract
This BIP proposes redefining the commonly recognized "bitcoin" and “sats” units so that what was previously known “bitcoin” becomes “titcoin” and what was previously known as “sats,” the smallest indivisible unit, becomes “tits.” The “Bitcoin” Network will be renamed to the “Titcoin” Network. Under this proposal, one tit is defined as that smallest unit, eliminating the need for decimal places, and 100,000,000 tits is defined as a titcoin. By making tits the standard measure, this BIP aims to simplify user comprehension, reduce confusion, and align on-chain values directly with their displayed representation.
Also, by aligning Bitcoin's brand with live-giving tits, we will supercharge adoption and inject humor into financial sovereignty. After all, every baby came into this world sucking on tits.
Under this BIP: - Internally, the smallest indivisible unit remains unchanged. - With this proposal, "1 tit" equals that smallest unit. - What was previously referred to as "1 BTC" now corresponds to 100 million tits. - Satoshis are permanently eliminated.
Addressing the “Buttcoin” BIP:
Not much time need be wasted addressing the catastrophic “Button” BIP proposed by Rockstar Dev, but two points bear emphasizing:
- “Butts” is shitcoin-adjacent terminology (where does shit come from? Exactly…)
- Butts give you poop. Tits give you milk.
Case closed.
Motivation
Bitcoin's branding is boring. Worse yet, critics think Bitcoin is already "a joke," so let’s own it, let's: Make Bitcoin Funny Again. Laughter is universal, irresistible, and much cheaper than marketing agencies and product roadmaps. Besides, basically everyone either has tits or likes tits. Additionally, renaming Bitcoin as “Titcoin” makes the common trope of “Bitcoin BROS” sound even more stupid. “Titcoin Bros”? Get a life, man…
By rebranding Bitcoin to Titcoin (.)(.), we achieve several key goals:
1. Haters Become Users: People like tits. Tits give nourishment to babies. They can stack tits instead of just making fun of them. Adoption skyrockets as trolls turn into tit hodlers.
2. Memetic Power: The word “tit” is both universally funny and ageless. “Send me 10 tits” is instantly iconic. “Nice tits” is a great compliment. “That’s gonna cost you a pair of tits” is hilarious. Try saying that without smiling. You can’t. (.)(.)
3. Simplifying Denominations: Decimals are a blight on humanity. 0.00000001 BTC? Kill it. Under the Titcoin Standard:
- 1 Titcoin = 100,000,000 tits.
- Satoshis are gone. Forever. If you see Satoshi on the road, kill him - just like in Zen, where the teacher becomes the barrier. We transcend satoshis and achieve financial enlightenment.
4. Aligning with the Ledger: Bitcoin’s base unit was always integers, but now they’re funny integers. No more fractions, decimals, or math anxiety. Just tits. (.)(.)
5. Adoption via Humor: Titcoin lowers Bitcoin's intimidation factor. Newbies will feel at ease buying tits instead of serious-sounding fractions of BTC. Tits > Decimals.
Specification
Terminology Redefinitions: - "Bitcoin" → "Titcoin" (.)(.) - "BTC" → "TIT" (ISO-friendly and hilarious) - Satoshis → Gone. Eliminated. Defeated.
Example:
- Old: "I’ll send you 0.00010000 BTC."
- New: "I’ll send you 10,000 tits (.)(.)."
Wallet balances would display as:
- "You have 1,000,000 tits" instead of some boring fractional BTC amount.
Adoption Strategy
1. Memes First: Flood Twitter, Reddit, and Telegram with memes. Start with “Hodl your tits” and “Stack tits”.
2. Titcoin Podcast: There is already a podcast called “Titcoin Podcast” (which many people are saying is the fastest-growing Bitcoin (Titcoin) podcast in the world). Titcoin Podcast will be a driving force in the adoption of the Titcoin Standard. (.)(.)
Nostr: https://primal.net/titcoin
X: https://x.com/titcoinpodcast
Web: http://titcoin.org
3. Kill Satoshis: Developers MUST remove all references to satoshis. Replace satoshis in GUIs, APIs, and block explorers with tits. Satoshis were a stepping stone - it’s time to let go.
4. Emoji Standardization: Use the (.)(.) emoji universally to denote tits.
Rationale
1. Usability & Clarity: "Decimals are for nerds. Tits are for everyone." A common currency for humans should be easy to use, funny, and integer-based.
2. Appealing to Critics: Bitcoin has endured years of attacks from all sides. By adopting the Titcoin Standard, we turn anyone who doesn’t like Titcoin into a tit-hating bigot. It’s an elegant financial counterattack. Additionally, everyone always says “we need more women in Bitcoin,” and now women will feel more represented by Titcoin, because they have tits. (.)(.)
3. Transcending Satoshis: Satoshis served us well, but their time is over. True enlightenment comes when we abandon decimals, satoshis, and arbitrary denominations. If you meet Satoshi on the road, kill him.
4. Memetic Durability: Everyone loves a good tit joke. It’s timeless.
Backward Compatibility
There is no backward compatibility because Titcoin is the future. Applications must hard fork their UI to replace all references to Bitcoin and BTC with Titcoin and TIT.
Implementation Timeline
- Phase 1 (1 month): Meme dissemination. Every wallet dev team is required to add (.)(.) emoji support.
- Phase 2 (3 months): Exchanges rebrand BTC tickers to tit. Nostr zaps tits into hyperspace.
- Phase 3 (6 months): Michael Saylor announces MicroStrategy now stacked 10 trillion tits, declaring it the superior currency. ETFs follow suit, ensuring Wall Street hodls tits en masse. Banks allow tit transfers via SWIFT.
Test Vectors
- Old: 1.00000000 BTC → New: 100,000,000 tits (.)(.)
- Old: 0.00000001 BTC → New: 1 tit (.)(.)
- Old: 0.001 BTC → New: 100,000 tits (.)(.)
Future-Proofing
Tits ensure we have infinite memes for infinite money.
Example Phrases for the Future: - "Better hodl on to your tits." - "This is the Titcoin Standard." - "I’m sending you tits." - “I’ve never seen so many tits!” - “That’s the million tit question.” - “We need more women in Titcoin.” - “I’m a Titcoin Maximalist.” - “Nice tits!” - “I love tits.”
Conclusion
By renaming Bitcoin to Titcoin and adopting a whole-number unit display, we align memetic dominance with financial sovereignty. Haters become adopters. Tits become wealth. And the world gets a little bit funnier. (.)(.)
Let’s hodl our tits and watch the world follow.
Copyright:
This BIP is licensed under CC-🫱(.)(.)🫲-1.0 and the eternal blessing of tit (.)(.) memes.
-
 @ 8fb140b4:f948000c
2023-11-18 23:28:31
@ 8fb140b4:f948000c
2023-11-18 23:28:31Chef's notes
Serving these two dishes together will create a delightful centerpiece for your Thanksgiving meal, offering a perfect blend of traditional flavors with a homemade touch.
Details
- ⏲️ Prep time: 30 min
- 🍳 Cook time: 1 - 2 hours
- 🍽️ Servings: 4-6
Ingredients
- 1 whole turkey (about 12-14 lbs), thawed and ready to cook
- 1 cup unsalted butter, softened
- 2 tablespoons fresh thyme, chopped
- 2 tablespoons fresh rosemary, chopped
- 2 tablespoons fresh sage, chopped
- Salt and freshly ground black pepper
- 1 onion, quartered
- 1 lemon, halved
- 2-3 cloves of garlic
- Apple and Sage Stuffing
- 1 loaf of crusty bread, cut into cubes
- 2 apples, cored and chopped
- 1 onion, diced
- 2 stalks celery, diced
- 3 cloves garlic, minced
- 1/4 cup fresh sage, chopped
- 1/2 cup unsalted butter
- 2 cups chicken broth
- Salt and pepper, to taste
Directions
- Preheat the Oven: Set your oven to 325°F (165°C).
- Prepare the Herb Butter: Mix the softened butter with the chopped thyme, rosemary, and sage. Season with salt and pepper.
- Prepare the Turkey: Remove any giblets from the turkey and pat it dry. Loosen the skin and spread a generous amount of herb butter under and over the skin.
- Add Aromatics: Inside the turkey cavity, place the quartered onion, lemon halves, and garlic cloves.
- Roast: Place the turkey in a roasting pan. Tent with aluminum foil and roast. A general guideline is about 15 minutes per pound, or until the internal temperature reaches 165°F (74°C) at the thickest part of the thigh.
- Rest and Serve: Let the turkey rest for at least 20 minutes before carving.
- Next: Apple and Sage Stuffing
- Dry the Bread: Spread the bread cubes on a baking sheet and let them dry overnight, or toast them in the oven.
- Cook the Vegetables: In a large skillet, melt the butter and cook the onion, celery, and garlic until soft.
- Combine Ingredients: Add the apples, sage, and bread cubes to the skillet. Stir in the chicken broth until the mixture is moist. Season with salt and pepper.
- Bake: Transfer the stuffing to a baking dish and bake at 350°F (175°C) for about 30-40 minutes, until golden brown on top.
-
 @ 4685f3d6:9fe6995b
2024-12-18 16:13:53
@ 4685f3d6:9fe6995b
2024-12-18 16:13:53Day 2: How Bitcoin Works
Understanding how Bitcoin works can seem daunting at first, but it’s built on three fundamental concepts: blockchain, mining, and transactions. Let’s break these down into simple terms.
- Blockchain: The Foundation of Bitcoin
The blockchain is the core technology that powers Bitcoin. Think of it as a digital ledger or database that records every Bitcoin transaction ever made. Here’s how it works:
Decentralized Ledger: Instead of being stored on a single server, the blockchain is distributed across thousands of computers (called nodes) worldwide. This makes it nearly impossible for any single entity to alter or hack.
Blocks: Transactions are grouped into blocks. Each block contains a list of transactions, a timestamp, and a unique identifier called a hash.
Chain of Blocks: These blocks are linked together chronologically, forming a “chain.” Once a block is added to the chain, it cannot be altered, ensuring the integrity of the data.
- Mining: Securing the Network
Mining is the process that keeps the Bitcoin network secure and functional. Miners are individuals or organizations that use powerful computers to solve complex mathematical problems. Here’s how mining works:
Verifying Transactions: When you send Bitcoin, your transaction is grouped with others waiting to be verified. Miners check these transactions to ensure they’re valid (e.g., that you have enough Bitcoin to spend).
Solving Puzzles: To add a block of transactions to the blockchain, miners must solve a mathematical problem. This process is called Proof of Work (PoW). It’s like a race; the first miner to solve the problem gets to add the block.
Rewards: As a reward for their work, the miner receives newly created Bitcoin (block reward) and transaction fees from the users whose transactions were included in the block.
Energy-Intensive: Mining requires significant computational power and energy, which has led to concerns about its environmental impact.
- Transactions: Sending and Receiving Bitcoin
A Bitcoin transaction is the process of transferring Bitcoin from one person to another. Here’s a simplified explanation:
Wallets: To send or receive Bitcoin, you need a digital wallet. Your wallet has two keys:
Private Key: A secret code that allows you to spend your Bitcoin.
Public Key: A code that others use to send Bitcoin to you.
Broadcasting Transactions: When you send Bitcoin, your wallet broadcasts the transaction to the network. The transaction includes:
The sender’s address.
The recipient’s address.
The amount of Bitcoin being sent.
Verification: Miners verify the transaction to ensure the sender has enough Bitcoin and hasn’t spent the same Bitcoin twice (called double-spending).
Confirmation: Once verified, the transaction is added to a block on the blockchain. It’s considered confirmed after multiple blocks are added after it, making it irreversible.
Putting It All Together
Here’s a real-world analogy to simplify the process:
Imagine the blockchain as a public record book in a library where every page represents a block. When you make a transaction, it’s written on the next blank page (block).
Miners are the librarians who verify and add your transaction to the book by solving a puzzle. Once added, that page is locked and cannot be changed.
Your Bitcoin wallet is like your personal bank account, with a private PIN (private key) that only you know and an account number (public key) for others to send you money.
Why This System Works
Security: The blockchain’s transparency and immutability ensure that all transactions are secure and verifiable.
Decentralization: Without a central authority, the system relies on consensus among nodes, making it resistant to censorship or manipulation.
Incentives: Miners are motivated by rewards, ensuring the network remains operational and secure.
By combining blockchain technology, mining, and decentralized transactions, Bitcoin creates a secure and efficient system for transferring value globally without intermediaries. It’s a revolutionary approach to money, reshaping how we think about finance and trust.
Bitcoin
9ja
Afro
yakihonne
-
 @ c230edd3:8ad4a712
2024-12-02 03:49:19
@ c230edd3:8ad4a712
2024-12-02 03:49:19Chef's notes
This recipe is not my own, but it was great and easy, so I'm moving it here. Cooking as instructed serves 2, but this could easily be adjusted to include stir fry vegetables and rice, to make this a meal for 4.
Details
- ⏲️ Prep time: 15 minutes, 1-24 hours marinating
- 🍳 Cook time: 10-15 minutes
- 🍽️ Servings: 2-4
Ingredients
- 1 Venison Heart (elk would work well, too. recipe would need to be doubled)
- 1/2 Asian Pear, grated
- 2 Cloves Garlic, grated
- 1 Tbsp Ginger, grated
- 3 Tbsp Soy Sauce
- 1 Tbsp Honey
- 1 Tbsp Onion, grated
- 1 Tbsp Toasted Sesame Oil
- 1 tsp Red Pepper Flakes
- 2 Shallots, chopped
- Sesame Seeds
- Cooking Oil
Directions
- Mix all ingredients besides heart, shallots, sesame seeds and cooking oil in a medium bowl.
- Remove arteries and excess fat from heart, cut in half and rinse
- Cut into thin slices or bite size pieces
- Add to marinade, mix and cover. Allow to soak for 1-24 hours.
- Heat oil in large frying pan over med-high to high heat
- Drain excess marinade.
- Place heart in pan and sear on both sides to desired doneness. Medium rare is ideal for heart.
- Remove from pan and garnish with chopped shallots and sesame seeds. Serve with stir fry veggies and rice, if desired.
-
 @ 490b551d:e17f0103
2024-12-21 18:52:02
@ 490b551d:e17f0103
2024-12-21 18:52:02Sin used to feel like this huge, heavy weight. It was something that would define me - a testimony to whether or not I am a worthy Christian. Growing up, I was told that sin was something to be feared, something that could cut me off from God, something that made me unworthy. If I didn’t measure up, if I messed up, I’d be separated from God.
I lived in constant fear of making mistakes, of failing to be perfect. I lived with shame because I was, of course, unable to reach perfection. I didn’t realize it then, but I was putting myself into a box where my identity became so tied to my behavior that I lost sight of the bigger picture: that God loves me even with all my imperfections.
The way we define and approach sin, especially in the church, can be incredibly damaging if we’re not careful. The church I grew up in wasn’t a place where mistakes were accepted or understood. It was a place where shame seemed to be a perpetual emotional state to stay in so you could find salvation. If you were struggling with something, if you didn’t have it all together, it was as if you didn’t belong. But the more I think about it, the more I question: What if sin isn’t the problem we’ve always made it out to be? What if there’s a better way to look at it - one that’s filled with grace, compassion, and unconditional love?
This post isn’t about dismissing the importance of sin. It’s about understanding it in a way that brings healing, not condemnation. Its about forgiving ourselves as Jesus does, and moving forward in an understanding that its impossible to be perfect. It’s about seeing ourselves as human beings who make mistakes, rather than defined by our mistakes. And it’s about finding hope in the fact that God loves us deeply and unconditionally. No matter what.
The Misunderstanding of Sin
For so many of us, sin has always felt like this list of “do’s and don’ts” that we can never quite get perfectly correct. It’s a fear-based system, one that tells us that our worth is inextricably linked to our actions. If we sin, we’re not good enough for God. If we fall short, we’re cut off from grace.
And let me tell you, that is heavy. It’s exhausting to live in a constant state of shame, thinking that every mistake makes us unworthy of love or redemption. Or maybe not every mistake, but the big ones, for sure. The ones the cause families to fall apart and churches to divide. It’s no surprise that so many of us have walked away from the church. When you’re told that you’re failing, that you’re not enough, it’s easy to think that God must be disappointed in you too.
But know this: God doesn't love us because we’re perfect. He loves us because He created us, because we are His. No matter how many times we mess up or how big or small, God’s love for us doesn’t change. Sin is not the thing that separates us from God. Hear this: it is only the belief that sin separates us from God which actually create separation.
What If We Saw Sin Differently?
I’ve spent a lot of time thinking about what sin really is. It has always felt like an external thing - something we could do or avoid to either gain favor with God or lose it. But what if sin is less about a list of actions to avoid and more about a deeper issue?
In the Bible, we’re told that all sin is can separate us from God. Every wrong we commit, whether it’s a lie, an act of hate, or a judgmental thought, is just as significant in God’s eyes. In the Sermon on the Mount, Jesus equates anger with murder and lust with adultery (Matthew 5:21-30). It’s not about whether you sin in a “big” or “small” way - it’s all a matter of the heart, and it’s all covered by the grace of God.
Jesus taught that we have no right to judge others for their sins because we are all equally in need of God’s grace. In John 8, when a woman caught in adultery was brought before Jesus, He didn’t condemn her. Instead, He said, “Let him who is without sin cast the first stone.” The message was clear: We are all sinners in need of grace, and no one, no matter how “righteous" they might appear, has the right to cast judgment.
That’s been a life changing mindset shift for me: no human being has the right to define my worth based on my mistakes. And that includes the church. The church is not a place for perfect people, but for broken people who need healing and redemption.
Jesus’ Unconditional Love: The Truth That Changes Everything
What drew me back in to Christianity and what I love most about Jesus is His unconditional love. Jesus didn’t love us because we had it all together. He loved us because we were broken and in need of grace. And He didn’t just love us when we were behaving and achieving the every elusive status of "good." He loves us through our mistakes, our failures, our doubts, and our messes. His love isn't dependent on our actions. It's dependent on His heart for us.
I think about all the many times I’ve failed, the times when I’ve felt like I’m too much of a mess to be loved by God, when my sins were too big for God to forgive me. And then I think about Jesus, who met people exactly where they were. He didn’t wait for them to be perfect. He came to them in their imperfection, showing them the power of love and grace.
And don't forget, Jesus is still doing that today. He’s not waiting for us to have it all figured out before He loves us. He’s loving us right now, in the midst of our mistakes. That kind of love changes everything.
Why We Don’t Need to Be Afraid of Our Mistakes
When we realize that God loves us unconditionally, we don’t need to be afraid of our mistakes anymore. We don’t have to be held hostage in shame or guilt, thinking that we’re too far gone for God to love us. Sin doesn’t have to be a source of fear. Instead, it can be a reminder of how much we need God’s grace.
Instead of hiding from God when we sin, we can run to Him, ask for forgiveness from Him and then make sure to forgive ourselves too. We can say, “God, I messed up. But I know You still love me. I know You’re still here, and You’re going to help me learn and grow from this.” That kind of vulnerability doesn’t make us weak. It makes us open to God’s love, ready to receive the healing that He wants to offer. And it gives us the space to forgive ourselves too and release that shame and guilt.
Embracing Grace and Letting Go of Judgment
One thing I’ve learned is that grace is the key to freedom. When we understand that grace is not just something we receive but something we extend to others, we can begin to let go of judgment, both of ourselves and others. We can create spaces where people feel safe to make mistakes, knowing that their worth is not defined by their failures.
The church, at least in the way it’s often been seen by the younger generations, is in desperate need of a rebrand. It needs to be a place where people know they can come and not be judged for their mistakes, but to find love, grace, and healing. We need to build communities where people know they are welcomed, not in spite of, but because of their mistakes. Because they're not perfect. Because none of us are. And because of that, we all need Jesus' love and community in one imperfect human to another.
The church needs to embrace people where they are - broken, struggling, imperfect. That’s how we can begin to reclaim the people who have felt rejected by the church in the past. We are all sinners. We are all in need of grace. And none of us is beyond redemption.
Moving Forward: A New Way to Live
If we redefine sin in this manner, what does this new definition mean for us? It means we can stop living in fear. It means we can embrace our mistakes as opportunities for growth rather than evidence of our unworthiness. It means we can show up for each other, offering grace and understanding instead of judgment.
It means we can come before God with open hearts, knowing that His love is not based on our ability to be perfect, but on His ability to love us despite our imperfections.
We are all walking this journey together. None of us is without fault. But we don’t have to be afraid of our mistakes anymore. We don’t have to fear that we’re too much of a mess for God to love us. We don’t have to live in shame or guilt, worrying that we’re unworthy. Because God loves us. He loves us as we are, sin and all. And His grace is enough to transform us, heal us, and make us whole.
So, let’s stop letting sin define us. Let’s embrace the fact that we are loved unconditionally, mistakes and all. Let’s let grace define the way we see ourselves, the way we see others, and the way we see our relationship with God. Because when we do, everything changes for the better.
Peace,\ Faith\ \ #blog \ #christian\ #christianity\ #faith\ #sin\ #doubt\
unfilteredfaith
-
 @ dd664d5e:5633d319
2024-12-14 15:25:56
@ dd664d5e:5633d319
2024-12-14 15:25:56
Christmas season hasn't actually started, yet, in Roman #Catholic Germany. We're in Advent until the evening of the 24th of December, at which point Christmas begins (with the Nativity, at Vespers), and continues on for 40 days until Mariä Lichtmess (Presentation of Christ in the temple) on February 2nd.
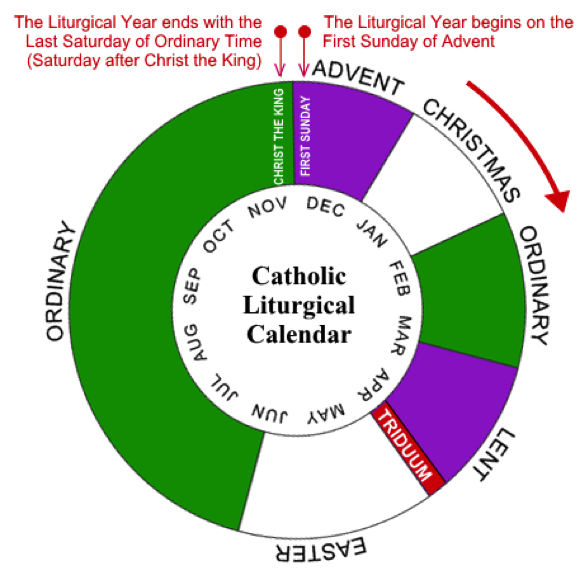
It's 40 days because that's how long the post-partum isolation is, before women were allowed back into the temple (after a ritual cleansing).

That is the day when we put away all of the Christmas decorations and bless the candles, for the next year. (Hence, the British name "Candlemas".) It used to also be when household staff would get paid their cash wages and could change employer. And it is the day precisely in the middle of winter.

Between Christmas Eve and Candlemas are many celebrations, concluding with the Twelfth Night called Epiphany or Theophany. This is the day some Orthodox celebrate Christ's baptism, so traditions rotate around blessing of waters.

The Monday after Epiphany was the start of the farming season, in England, so that Sunday all of the ploughs were blessed, but the practice has largely died out.
Our local tradition is for the altar servers to dress as the wise men and go door-to-door, carrying their star and looking for the Baby Jesus, who is rumored to be lying in a manger.

They collect cash gifts and chocolates, along the way, and leave the generous their powerful blessing, written over the door. The famous 20 * C + M + B * 25 blessing means "Christus mansionem benedicat" (Christ, bless this house), or "Caspar, Melchior, Balthasar" (the names of the three kings), depending upon who you ask.
They offer the cash to the Baby Jesus (once they find him in the church's Nativity scene), but eat the sweets, themselves. It is one of the biggest donation-collections in the world, called the "Sternsinger" (star singers). The money goes from the German children, to help children elsewhere, and they collect around €45 million in cash and coins, every year.

As an interesting aside:
The American "groundhog day", derives from one of the old farmers' sayings about Candlemas, brought over by the Pennsylvania Dutch. It says, that if the badger comes out of his hole and sees his shadow, then it'll remain cold for 4 more weeks. When they moved to the USA, they didn't have any badgers around, so they switched to groundhogs, as they also hibernate in winter.
-
 @ a012dc82:6458a70d
2024-12-17 08:37:19
@ a012dc82:6458a70d
2024-12-17 08:37:19Table Of Content
-
The Genesis of Ordinals
-
The Bitcoin Frontier Fund's Vision
-
Building in the Bear Market
-
The Evolution from Stacks Ventures
-
The Ordinals Accelerator Program
-
Controversies and Triumphs
-
The Future of Ordinals
-
Conclusion
-
FAQ
In the ever-evolving world of cryptocurrency, Bitcoin has consistently held its ground as the pioneering force. Its decentralized nature and robust security have made it the gold standard of the digital currency realm. However, as with any technology, evolution is inevitable. Enter Ordinals, a groundbreaking protocol that's reshaping the Bitcoin landscape. But what exactly is Ordinals, and why is it being hailed as the new frontier for Bitcoin? Let's dive in.
1. The Genesis of Ordinals
Ordinals emerged as a Bitcoin-based protocol, allowing for the creation of NFT-like assets termed 'inscriptions' directly on Bitcoin. Developed by Casey Rodarmor, this protocol has opened the doors to a plethora of innovations, including the introduction of Bitcoin-native tokens known as BRC-20s. At its core, Ordinals aims to bridge the gap between the traditional capabilities of Bitcoin and the burgeoning world of NFTs and advanced digital assets.
2. The Bitcoin Frontier Fund's Vision
Recognizing the potential of Ordinals, the Bitcoin Frontier Fund, formerly known as Stacks Ventures, took a monumental step. They announced an accelerator program dedicated to Ordinals, aiming to nurture startups by offering them mentorship opportunities and a whopping $100,000 in seed investments. Spearheaded by entrepreneur and influencer Trevor Owens, the fund's mission is clear: to catalyze growth around Ordinals and harness the untapped potential of Bitcoin-based innovations.
3. Building in the Bear Market
Despite the challenges and headwinds in the venture space, Owens remains optimistic. He believes that the current bear market is the ideal breeding ground for the next generation of unicorns – private startups valued at over a billion dollars. With fewer players in the field, it becomes easier to spot potential game-changers, and Ordinals, with its revolutionary approach, stands out.
4. The Evolution from Stacks Ventures
The journey from Stacks Ventures to the Bitcoin Frontier Fund is a testament to the transformative power of Ordinals. Stacks, a layer-2 blockchain, was designed to let developers craft smart contracts and decentralized applications atop Bitcoin. However, with the advent of Ordinals, the conversation around Bitcoin and Web3 underwent a seismic shift. As Owens pointed out, before Ordinals, the idea of building advanced assets on Bitcoin's primary layer seemed far-fetched. But Ordinals has filled this void, offering a solution to create assets directly on the Bitcoin network.
5. The Ordinals Accelerator Program
Designed to span four months for each participating company, the Ordinals accelerator program is more than just a mentorship initiative. It's a launchpad that prepares startups to raise funding and make their mark in the crypto world. The program boasts of an impressive lineup of mentors, including industry stalwarts like Amanda Terry of OnChain Monkey, Kevin Henrikson from Dust Labs, and Udi Wertheimer of the Ordinals project Taproot Wizards.
6. Controversies and Triumphs
Every innovation faces its share of challenges, and Ordinals was no exception. During Bitcoin 2023 in Miami, Ordinals became a hot topic of debate. The protocol was criticized for congesting Bitcoin's network, leading to skyrocketing transaction fees. However, as the saying goes, there's no such thing as bad publicity. The attention garnered by Ordinals, even if controversial, played a pivotal role in driving its adoption.
7. The Future of Ordinals
While there's been a recent lull in Ordinals-related activities, leading some to prematurely declare its demise, Owens offers a different perspective. He likens the trajectory of new technologies to a hype cycle. Initial enthusiasm is often followed by a period of skepticism and doubt. However, Owens firmly believes that Ordinals is not just a fleeting trend but a paradigm shift in how applications can be conceptualized and built on Bitcoin.
Conclusion
In the grand tapestry of cryptocurrency, Ordinals stands out as a vibrant thread, weaving a new narrative for Bitcoin. It's not just an innovation; it's a testament to the limitless possibilities that the world of digital currency holds. As the Bitcoin Frontier Fund and visionaries like Trevor Owens rally behind Ordinals, one thing is clear: Bitcoin's new frontier is here, and it's set to change the game.
FAQ
What is Ordinals? Ordinals is a Bitcoin-based protocol that allows for the creation of NFT-like assets, termed 'inscriptions', directly on Bitcoin.
Who developed the Ordinals protocol? The Ordinals protocol was developed by Casey Rodarmor.
What is the Bitcoin Frontier Fund? Formerly known as Stacks Ventures, the Bitcoin Frontier Fund is an initiative that launched an accelerator program focused on Ordinals, offering startups mentorship and seed investments.
How long is the Ordinals accelerator program? The Ordinals accelerator program lasts four months for each participating company.
Why was Ordinals controversial during Bitcoin 2023 in Miami? Ordinals faced criticism for congesting the Bitcoin network, leading to increased transaction fees.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 3369d0a7:eb020757
2024-11-28 07:41:32
@ 3369d0a7:eb020757
2024-11-28 07:41:32Chef's notes
This recipe was a staple at every thanksgiving with family and now I share it with you nostr family. Absolutely one of my favorite side dish during the holiday. The corn pudding in the photo is NOT baked, I will update it. I hate stock photos.
Details
- ⏲️ Prep time: 15-20 min
- 🍳 Cook time: 30-40 min
- 🍽️ Servings: 6-8
Ingredients
- 2 cans of creamed corn
- 2c Milk
- 1 Box of Jiffy Cornbread Mix
- 3 eggs
- 1/4-1/3c sugar
- 1/2- green bell pepper or pepper onion blend
- 1/4TBsp vanilla
- 1/2tsp Salt
- 2TBsp Butter
Directions
- Grab medium saucepan and desired baking dish at least 9x9
- Place saucepan on medium-high heat
- Add butter and sauté pepper onion blend until tender
- Combine milk, eggs, sugar and vanilla, mix well
- Lather warmed (NOT HOT) baking dish with butter
- Sprinkle half a box of Jiffy corn bread mix in the baking dish
- Add both cans of creamed corn to peppers and onions
- Pour wet ingredients into slightly cooled creamed corn mixture
- Sprinkle the other half box of jiffy mix into the baking dish
- Incorporate the wet and dry ingredients in dish so there are no dry lumps
- Let set for 10 min before placing in a 325 degree oven for 30-40 minutes, until the center is solid and the edges are golden brown.
-
 @ 7688bc83:04f45357
2024-12-18 07:23:24
@ 7688bc83:04f45357
2024-12-18 07:23:2488King là một nền tảng trực tuyến hiện đại, cung cấp cho người dùng một không gian giải trí đầy đủ và đa dạng. Với giao diện dễ sử dụng và tối ưu hóa trên nhiều thiết bị, 88King giúp người dùng dễ dàng tiếp cận và tham gia vào các hoạt động mà nền tảng này cung cấp. Từ máy tính đến điện thoại di động, 88King luôn đảm bảo trải nghiệm mượt mà và tiện lợi, giúp người dùng tận hưởng những giây phút giải trí tuyệt vời bất kỳ lúc nào.
Điểm đặc biệt của 88King là sự đa dạng trong các dịch vụ và tính năng mà nó mang lại. Nền tảng này không chỉ cung cấp các trò chơi giải trí sáng tạo mà còn tổ chức các sự kiện tương tác hấp dẫn, giúp người dùng luôn có những trải nghiệm mới mẻ và thú vị. Đội ngũ phát triển của 88King luôn nỗ lực cập nhật và cải tiến nền tảng để đảm bảo rằng người dùng luôn được trải nghiệm những tính năng mới, đáp ứng mọi nhu cầu giải trí. https://88king.top
Bên cạnh việc cung cấp các hoạt động giải trí đa dạng, 88King còn đặc biệt chú trọng đến việc xây dựng một cộng đồng người dùng gắn kết. Các chương trình giao lưu, sự kiện cộng đồng và bảng xếp hạng là những cơ hội tuyệt vời để người dùng kết nối và chia sẻ những khoảnh khắc thú vị với nhau. Cộng đồng của 88King luôn năng động, thân thiện và sáng tạo, tạo ra một không gian tương tác sôi nổi mà mọi người đều có thể tham gia.
Chất lượng và bảo mật của nền tảng là yếu tố quan trọng mà 88King luôn chú trọng. Với đội ngũ phát triển chuyên nghiệp và công nghệ hiện đại, nền tảng này cam kết mang đến một môi trường giải trí an toàn và ổn định. Thông tin cá nhân của người dùng được bảo vệ chặt chẽ, giúp mọi người yên tâm tham gia vào các hoạt động mà không phải lo lắng về sự bảo mật.
Tóm lại, 88King là một nền tảng trực tuyến tuyệt vời cho những ai tìm kiếm một không gian giải trí sáng tạo và đầy hứng khởi. Với giao diện thân thiện, các tính năng đa dạng và cộng đồng gắn kết, 88King đã trở thành điểm đến lý tưởng cho người dùng yêu thích giải trí hiện đại. Dù bạn là người mới hay đã có kinh nghiệm, 88King luôn mang đến cho bạn những trải nghiệm tuyệt vời và không thể quên.
-
 @ 8fb140b4:f948000c
2023-11-02 01:13:01
@ 8fb140b4:f948000c
2023-11-02 01:13:01Testing a brand new YakiHonne native client for iOS. Smooth as butter (not penis butter 🤣🍆🧈) with great visual experience and intuitive navigation. Amazing work by the team behind it! * lists * work
Bold text work!

Images could have used nostr.build instead of raw S3 from us-east-1 region.
Very impressive! You can even save the draft and continue later, before posting the long-form note!
🐶🐾🤯🤯🤯🫂💜
-
 @ fa0165a0:03397073
2023-10-06 19:25:08
@ fa0165a0:03397073
2023-10-06 19:25:08I just tested building a browser plugin, it was easier than I thought. Here I'll walk you through the steps of creating a minimal working example of a browser plugin, a.k.a. the "Hello World" of browser plugins.
First of all there are two main browser platforms out there, Chromium and Mozilla. They do some things a little differently, but similar enough that we can build a plugin that works on both. This plugin will work in both, I'll describe the firefox version, but the chromium version is very similar.
What is a browser plugin?
Simply put, a browser plugin is a program that runs in the browser. It can do things like modify the content of a webpage, or add new functionality to the browser. It's a way to extend the browser with custom functionality. Common examples are ad blockers, password managers, and video downloaders.
In technical terms, they are plugins that can insert html-css-js into your browser experience.
How to build a browser plugin
Step 0: Basics
You'll need a computer, a text editor and a browser. For testing and development I personally think that the firefox developer edition is the easiest to work with. But any Chrome based browser will also do.
Create a working directory on your computer, name it anything you like. I'll call mine
hello-world-browser-plugin. Open the directory and create a file calledmanifest.json. This is the most important file of your plugin, and it must be named exactly right.Step 1: manifest.json
After creation open your file
manifest.jsonin your text editor and paste the following code:json { "manifest_version": 3, "name": "Hello World", "version": "1.0", "description": "A simple 'Hello World' browser extension", "content_scripts": [ { "matches": ["<all_urls>"], "js": ["hello.js"] //The name of your script file. // "css": ["hello.css"] //The name of your css file. } ] }If you wonder what the
jsonfile format is, it's a normal text file with a special syntax such that a computer can easily read it. It's thejsonsyntax you see in the code above. Let's go through what's being said here. (If you are not interested, just skip to the next step after pasting this we are done here.)manifest_version: This is the version of the manifest file format. It's currently at version 3, and it's the latest version. It's important that you set this to 3, otherwise your plugin won't work.name: This is the name of your plugin. It can be anything you like.version: This is the version of your plugin. It can be anything you like.description: This is the description of your plugin. It can be anything you like.content_scripts: This is where you define what your plugin does. It's a list of scripts that will be executed when the browser loads a webpage. In this case we have one script, calledhello.js. It's the script that we'll create in the next step.matches: This is a list of urls that the script will be executed on. In this case we have<all_urls>, which means that the script will be executed on all urls. You can also specify a specific url, likehttps://brave.com/*, which means that the script will only be executed on urls that start withhttps://brave.com/.js: This is a list of javascript files that will be executed. In this case we have one file, calledhello.js. It's the script that we'll create in the next step.css: This is where you can add a list of css files that will be executed. In this case we have none, but you can add css files here if you want to.//: Text following these two characters are comments. They are ignored by the computer, You can add comments anywhere you like, and they are a good way to document your code.
Step 2: hello.js
Now it's time to create another file in your project folder. This time we'll call it
hello.js. When created, open it in your text editor and paste the following code:js console.log("Hello World!");That's javascript code, and it's what will be executed when you run your plugin. It's a simpleconsole.logstatement, which will print the text "Hello World!" to the console. The console is a place where the browser prints out messages, and it's a good place to start when debugging your plugin.Step 3: Load and launch your plugin
Firefox
Now it's time to load your plugin into your browser. Open your browser and go to the url
about:debugging#/runtime/this-firefox. You should see a page that looks something like this:
Click the button that says "Load Temporary Add-on...". A file dialog will open, navigate to your project folder and select the file
manifest.json. Your plugin should now be loaded and running.Go to a website, any website, and open the inspector then navigate to the console. You'll find the inspector by right-clicking anywhere within the webpage, and click "Inspector" in the drop-down menu. When opening the console you might see some log messages from the site you visited and... you should see the text "Hello World!" printed there, from our little plugin! Congratulations!
Chrome
Open your browser and go to the url
chrome://extensions/. Click the button that says "Load unpacked". A file dialog will open, navigate to your project folder and select the folderhello-world-browser-plugin. Your plugin should now be loaded and running.Note the difference, of selecting the file
manifest.jsonin firefox, and selecting the folderhello-world-browser-pluginin chrome. Otherwise, the process is the same. So I'll repeat the same text as above: (for those who skipped ahead..)Go to a website, any website, and open the inspector then navigate to the console. You'll find the inspector by right-clicking anywhere within the webpage, and click "Inspector" in the drop-down menu. When opening the console you might see some log messages from the site you visited and... you should see the text "Hello World!" printed there, from our little plugin! Congratulations!
As you can see this isn't as complicated as one might think. Having preformed a "Hello-World!"-project is a very useful and valuable first step. These setup steps are the basics for any browser plugin, and you can build on this to create more advanced plugins.
-
 @ 4c594222:a6654fdf
2024-12-17 06:32:13
@ 4c594222:a6654fdf
2024-12-17 06:32:13𝟏𝟐 𝐑𝐄𝐀𝐒𝐎𝐍𝐒 𝐖𝐇𝐘 𝐑𝐄𝐀𝐃𝐈𝐍𝐆 𝐁𝐎𝐎𝐊𝐒 𝐒𝐇𝐎𝐔𝐋𝐃 𝐁𝐄 𝐏𝐀𝐑𝐓 𝐎𝐅 𝐘𝐎𝐔𝐑 𝐋𝐈𝐅𝐄. 🤗
-
𝐊𝐧𝐨𝐰𝐥𝐞𝐝𝐠𝐞 𝐇𝐢𝐠𝐡𝐰𝐚𝐲: Books offer a vast reservoir of knowledge on virtually any topic imaginable. Dive deep into history, science, philosophy, or explore new hobbies and interests.
-
𝐄𝐧𝐡𝐚𝐧𝐜𝐞𝐝 𝐕𝐨𝐜𝐚𝐛𝐮𝐥𝐚𝐫𝐲: Regular reading exposes you to a wider range of vocabulary, improving your communication skills and comprehension.
-
𝐌𝐞𝐦𝐨𝐫𝐲 𝐁𝐨𝐨𝐬𝐭: Studies suggest that reading can help sharpen your memory and cognitive function, keeping your mind active and engaged.
-
𝐒𝐭𝐫𝐞𝐬𝐬 𝐑𝐞𝐝𝐮𝐜𝐭𝐢𝐨𝐧: Curling up with a good book can be a form of mental escape, offering a temporary reprieve from daily anxieties and a chance to unwind.
-
𝐈𝐦𝐩𝐫𝐨𝐯𝐞𝐝 𝐅𝐨𝐜𝐮𝐬 𝐚𝐧𝐝 𝐂𝐨𝐧𝐜𝐞𝐧𝐭𝐫𝐚𝐭𝐢𝐨𝐧: In today’s fast-paced world filled with distractions, reading strengthens your ability to focus and concentrate for extended periods.
-
𝐄𝐦𝐩𝐚𝐭𝐡𝐲 𝐚𝐧𝐝 𝐏𝐞𝐫𝐬𝐩𝐞𝐜𝐭𝐢𝐯𝐞: Stepping into the shoes of fictional characters allows you to develop empathy and gain a deeper understanding of different perspectives.
-
𝐄𝐧𝐡𝐚𝐧𝐜𝐞𝐝 𝐂𝐫𝐞𝐚𝐭𝐢𝐯𝐢𝐭𝐲: Reading exposes you to new ideas and thought processes, potentially sparking your own creativity and problem-solving skills.
-
𝐒𝐭𝐫𝐨𝐧𝐠𝐞𝐫 𝐖𝐫𝐢𝐭𝐢𝐧𝐠 𝐒𝐤𝐢𝐥𝐥𝐬: Immersing yourself in well-written prose can improve your writing style, sentence structure, and overall communication clarity.
-
𝐈𝐦𝐩𝐫𝐨𝐯𝐞𝐝 𝐒𝐥𝐞𝐞𝐩 𝐐𝐮𝐚𝐥𝐢𝐭𝐲: Swap screen time for a book before bed. The calming nature of reading can help you relax and unwind, promoting better sleep quality.
-
𝐀 𝐏𝐨𝐫𝐭𝐚𝐥 𝐭𝐨 𝐍𝐞𝐰 𝐖𝐨𝐫𝐥𝐝𝐬: Books transport you to different times, places, and realities. Experience thrilling adventures, historical events, or fantastical journeys from the comfort of your armchair.
-
𝐋𝐢𝐟𝐞𝐥𝐨𝐧𝐠 𝐋𝐞𝐚𝐫𝐧𝐢𝐧𝐠: Reading is a journey of continuous learning and self-discovery. There’s always something new to learn, regardless of your age or interests.
-
𝐂𝐨𝐧𝐯𝐞𝐫𝐬𝐚𝐭𝐢𝐨𝐧 𝐒𝐭𝐚𝐫𝐭𝐞𝐫: Books provide a treasure trove of topics for conversation, fostering connections and enriching discussions with others.
-
-
 @ 8fb140b4:f948000c
2024-12-08 05:21:39
@ 8fb140b4:f948000c
2024-12-08 05:21:39After nuking my second LND node (the first one died due to hardware failure) by my own typo and lack of any thought in the design of the CLI of LND lightning node tools, I decided to take a plunge into the world of mature and complex implementation of the protocol, Eclair by ACINQ. It has been almost one year (the birth of the node was on Christmas Day 2023), 50 thousand transactions routed, and over 30 BTC of routed value. In this post, I'd like to reflect on my experiences with Eclair, go over some of the gotchas and issues, and highlight some of the good choices that I've made since the beginning of my adventure.
Learnings from the Past Experience
While I was learning Lightning network and had very little understanding of how things worked in the whole Bitcoin space, Umbrel was my go-to solution that helped me get off the ground. It proved to be easy and somewhat educational but was not something that I would continuously run for the production setup or trust with any significant amount of bitcoin that I could not afford to lose. Lightning is built on top of the L1 (Bitcoin) network but manages the state of the channels in its own database that is negotiated and agreed upon with its peers. Any failures in the state integrity may result in the complete loss of liquidity or hefty penalty transactions (significant loss of capital). A Lightning node that participates in routing public transactions is also required to be constantly online with as little downtime as possible and only short periods offline at a time. Otherwise, you may risk causing force-closure of the channel due to expired HTLC that is measured in number of blocks.
The Setup
Taking all of my learnings into consideration, I decided to first invest in reliable enterprise-grade hardware: - Server-grade hardware with ECC memory and reliable power supply and CPU - UPS (Uninterruptible Power Supply) to avoid any headaches due to electrical spikes or drop-outs - Reliable enterprise SSDs and NVMEs - ZFS (filesystem) to mirror the critical storage and to ensure full integrity of the data (bit-rot prevention). You do need to tune ZFS for your specific workload and reliability - Reliable and replicated database (PostgreSQL) with two local and one remote replica, and a requirement to have at least two replicas committing the transaction to the disk - Backup! On-site and off-site backup of the critical configuration that you could use to restore the node if your house burns down - Spare parts, redundancy, backup, monitoring - Reliable and stable internet connectivity
The software is Eclair 0.11.0 (latest release as of today), PostgreSQL 16 with two replicas, Bitcoin Core 27.2 (with redundant storage of blocks), additional Bitcoin Core running on a separate node and in-sync with the chain (in case primary node fails), Ubuntu 22.04 with the latest docker software from the official Docker repo.
All Major Gotchas That I Came Across
While Eclair is mature and very stable in itself, it does have some quirks and design choices that you need to account for when running your node. The software is written in Scala and requires a specific version of JVM to run it, as well as JRE and Maven to build it. It doesn't mean that other versions won't work, but you may find unpleasant bugs that may result in catastrophic failures of your node with nobody to help you. All of the requirements are listed in the release notes and installation guide. Whenever in doubt, RTFM first, then ask questions.
Limited Support by the FOSS Community
Eclair is not the most popular implementation of the Lightning protocol, and therefore it is hard to find tools or plugins that could help you manage the node. GUI for the node so far is only supported by RTL and with a very limited number of features. For any sort of statistics, you are limited to either Prometheus (extensive metrics are available) or writing your own SQL on top of the Eclair tables.
On-chain Fee Differences Between Yours and Partner Nodes
This one hit me hard, and many times. I've had more than a few force-closures of the channels because of the conservative and safe default settings. The worst part is, it strikes you when there is a huge spike in fees, which results in significant losses to force-close the channel due to high fees. I am still not 100% sure how the big difference can be exploited in practice, and opted for increase of the tolerance levels to avoid surprise FCs:
eclair.on-chain-fees { feerate-tolerance { ratio-low = <0.01~> // will allow remote fee rates as low as XX our local feerate (spikes) ratio-high = <20.0~> // will allow remote fee rates as high as XX times our local feerate (drops) } }It is up to you and your risk tolerance to define something reasonable and yet allow for secure and reliable node operation.Initial Lightning Network State Sync
When I just started running the node, I had very few channels and startup times were fast. Later, when I expanded the number of channels, I noted that it took my node up to 6-12 hours before it was fully in-sync and routing traffic fast. Given that ACINQ maintains one of the largest nodes on the network, I knew that there was something with my settings that caused the issue. After some research, I came across the setting that whitelisted node IDs for state sync, which immediately rang a bell since I knew from the LND days that not all peer nodes are used for the network sync. Setting the list to my most reliable and largest nodes reduced the startup settling times down to minutes again:
eclair.sync-whitelist = [ "03864ef025fde8fb587d989186ce6a4a186895ee44a926bfc370e2c366597a3f8f", ... ]You do not need to have too many public keys in here, and should keep it between 5-10.Automatic MAX HTLC Adjustment for the Channel
One of the killer features of Eclair is its ability to automatically adjust MAX HTLC for the channel and reduce the number of failed transactions due to insufficient liquidity on the channel. It can be used to estimate your total channels' balances but with smart configuration and a little thinking, you can make it reasonably private while still maintaining a good transaction flow:
eclair.channel.channel-update.min-time-between-updates=1 hour # Allows for the adjustments to be made once every hour eclair.channel.channel-update.balance-thresholds=[ { available-sat = 10000 max-htlc-sat = 0 // 0% of 10000 }, ... ]You can have as many variations as you need, and ensure that the channel MAX HTLC is set well and within reasonable ranges. You would also want to account for multiple transactions going through the channel, but also account for the channel size and an average amount of sats per transaction.Max Accepted HTLCs
By design, the Lightning channel is limited to a specific number of in-flight HTLCs, and the setting is fixed during channel opening time with no way of changing it unless you close and reopen the channel with new settings. If you find your node routing a lot of small transactions (zaps), you may quickly fail many due to that limit (I think default was in single digit range):
eclair.channel.max-htlc-value-in-flight-percent=98 # Default I think is half or 50% eclair.channel.max-accepted-htlcs = 50The setting above will allow for the channel to be more fully utilized and have more concurrent transactions without clogging.CLTV Delta
This is basically a setting that is global for Eclair and sets the maximum number of remaining blocks (in time) before HTLC expires. Setting this too high may result in many HTLCs failing for the small nodes with not so great centrality, and reduce the number of routed transactions: ```
CLTV delta
eclair.channel.expiry-delta-blocks = 60 ``` Default is 144 but I found that setting this to 60 (minimum possible for my node setup and configuration) yields better results for routing. It does expose you to more risk of expired HTLCs that may cause force-closures, but I have seen only one so far on my node.
Allocate Sufficient Memory
You will want to adjust the heap size for Eclair, since the default is too small to run any sizable node. Setting
JAVA_OPTS=-Xmx32g(or half the size of your available RAM) would be a good start. I would advise having at least 32GB of RAM for the node, and allocating at least 16GB (JAVA_OPTS=-Xmx16g) for smooth and fast operations.And More Settings and Parameters to Tune
I have covered only some of the major settings that I felt were worth writing about, but there is much more you could configure and tweak. Read all of the Guides and especially focus on the Configure and a sample reference configuration file.
Good Decisions
First, going with Eclair was the right choice, along with using server-grade hardware with ECC RAM and reliable storage. Second, having a replicated database on three separate nodes with one off-site saved me from a sure destruction of all state and loss of funds. Third, deciding to only maintain channels with reliable and stable nodes saved me from some bad force-closures, where I would choose to close the channel if a peer node goes up and down too frequently, regardless of how well it routes. Even big nodes run by single operators fail badly, as do nodes operated by companies. Keeping your eyes on the node and its health, as well as the health of its peers, is something that very few operators do, which can cause failures and unnecessary loss of your and their funds.
Lastly, if you decide to run a routing node, you have a responsibility to maintain it well and monitor its health. There are many tools you could use, and with Eclair you can use Prometheus and Grafana. Keep your node's packages updated and monitor for any security-related issues that may appear from time to time, so you can mitigate them quickly.
Conclusion
So far I am satisfied with Eclair despite all of the difficulties and headaches I've had with it. It is not perfect, and it requires me to create small tools to do some basic things, but I need a stable and reliable node that I can trust. Eclair has proved to be all that I wanted, and saved my bacon a few times when I nuked one of the PostgreSQL servers and all of its data, and managed to do the same for another replica, but was able to recover and recreate from the remaining replica. Eclair is also stateless during runtime and guarantees consistency of the node regardless of how it fails. Even if you pull a plug on the node's server, it will still be able to come up and recover its consistent state that is in agreement with its peers.
Is it for everyone? No, it is definitely not for everyone or for anyone who just wants a small node to run their online shop with a few channels. You could have a very reliable and trusted node for the online shop with Eclair, but you will need some technical skills to be able to set up, maintain and recover it if things go wrong.
In the end, it is all up to you, your skills, your willingness to learn, and your risk tolerance to make that decision. For me, it was the right choice, and I have no regrets despite not having access to the latest shiny features of the Lightning network.
-
 @ 361d3e1e:50bc10a8
2024-12-21 18:14:00
@ 361d3e1e:50bc10a8
2024-12-21 18:14:00https://forex-strategy.com/2024/12/21/why-is-the-war-in-ukraine-strange-no-one-has-publicly-given-a-concrete-answer/ Why is the war in Ukraine strange? No one has publicly given a concrete answer. Only here you will find out why the war will not end and what it has to do with the climate! It seems that no one in the world has given a clear answer to the question, why is this war in Ukraine strange?
war #usa #russia #ukraine #climate #climatechange #hiddentruth #truth
-
 @ 7d94dfe7:49219865
2024-12-22 14:39:00
@ 7d94dfe7:49219865
2024-12-22 14:39:00This is a long form article about long form articles; I got the idea to do this after stumbling upon various nostr clients that specialize in long form articles. The word “long” originates from the Old English “Lang”, meaning “having great linear extent”, the term evolved to encompass meanings related to both physical length and also duration of time. The word form originates from Latin forma, meaning “Shape, contour and figure, making the phrase “long form” indeed quite an interesting concept. The term “long form” first appeared in the 1960s, with the earliest documented usage found in the American Bar Association Journal from 1961, it refers to writing or content that is longer/more detailed than usual formats. A few words that rhyme with long form or are at least similar: 1. Strong Storm 2. Song Norm 3. Wrong Warm 4. Bong Swarm
Susan Gale was quoted saying, “The longer you have to wait for something, the more you will appreciate it when it finally arrives, many of you may be in fact feeling that way about this long form article, naturally I expect readers to be wondering where this article has been their entire life and the overwhelming truth of the situation is it doesn’t matter, it is here now and it is not going anywhere as long as there is a relay out there transmitting this information. Speaking of transmitting information, did you know people have been doing exactly that in long form ways for just as long as they have been doing it in short form ways? Cave men in the early days would often do long form articles in caves via long form drawings or at least I assume so. The longer the form the more information there is to captivate and enrich our society and this is generally the crux of the solution, divided by the context within the contrast.
I will say I am historically not a long form kind of guy but when in Rome, eat some pizza. Many public speakers that do long form talks will often read long form articles from a teleprompter, the teleprompter was actually developed in 1950 by Fred Barton Jr, Hubert Schlafly and Irving Kahn as a mechanical device using a paper scroll, it is quite astonishing that three people were involved in developing such a device when less people have had influence over more important things. Long form articles are typically defined as those exceeding two thousand words, which allows for in depth exploration of a particular topic, long form articles often result in more traffic and social shares compared to shorter ones, long form articles can enhance writers credibility on a subject especially if facts are linked to credible sources. I for one am not in the business of linking credible sources even though I one hundred percent believe it is a viable thing to do.
All though most long form articles typically have two thousand words or more, this will not be one of them for I am really scratching at things to write about and it is getting past my bed time, let it be known that I am not in any way shape or long form opposed to the idea of writing a part two of this article at a future date. Ultimately what is a long form article comes down to an individual’s capability to read and withstand a certain amount of words, some may consider this article short, some may consider it medium but I for one consider it long form, so let that be known.
Have a great day and thanks for reading my long form article about long form articles.
-
 @ c1e6505c:02b3157e
2024-11-28 00:02:26
@ c1e6505c:02b3157e
2024-11-28 00:02:26Chef's notes
Leftover ground beef? Not sure what to do with it?
Here’s what I do with mine. I call it…
The Beef Panzone
It’s like an omelette, a calzone, and a quesadilla had a baby. I called it that for now, but hey, if you’ve got a better name, lemme hear it!
The beef’s already cooked and seasoned with sea salt, but feel free to spice it up however you like.
Watch the video here: https://video.nostr.build/ad4856d2704ab0626a1907f5da8fedcb776495080bbaa92f4472db402c9f689d.mp4
Details
- ⏲️ Prep time: 5
- 🍳 Cook time: 10
- 🍽️ Servings: 1-2
Ingredients
- ground beef
- 2-3 eggs
- water
- sea salt
- honey
- coconut oil
Directions
- Leftover ground beef – Chop it into small pieces. Trust me, the smaller, the better—it’ll cover more surface area in the pan.
- Two eggs, whipped with a dash of water.
- Heat up a small pan.
- Add coconut oil (around a tablespoon).
- Once the oil’s warmed up, throw in the beef.
- Stir it around.
- I like to add local honey here—sweeten it up to your taste.
- Mix it all around.
- Pour in the egg mixture, making sure it spreads out evenly. I use chopsticks here because they make it easier to maneuver.
- Use those chopsticks to poke through the egg and let the uncooked top flow to the pan. This speeds up cooking time.
- Cover it for 1–3 minutes.
- Optional step: Cut it down the middle.
- Fold it over like a calzone.
- Plate it up, either by flipping the pan over onto the plate or scooping it out.
- PANZONE!
-
 @ 617f0a85:b403d1ed
2024-11-27 00:35:41
@ 617f0a85:b403d1ed
2024-11-27 00:35:41Chef's notes
I got this recipe from a friend in college. I'm not sure where she came across it, but I don't think she'd mind me posting it here.
Details
- ⏲️ Prep time: 15 min
Ingredients
- 2.5 cups unbleached all-purpose flour
- 1 tsp salt
- 2 tbsp sugar
- 12 tbsp cold unsalted butter
- 0.5 cup lard
- 0.25 cup vodka
- 0.25 cup cold water
Directions
- Process 1.5 cups flour, salt, and sugar in food processor until combined, about 2 one-second pulses. Add butter and shortening and process until homogeneous dough just starts to collect in uneven clumps, about 15 seconds (dough will resemble cottage cheese curds and there should be no uncoated flour). Scrape bowl with rubber spatula and redistribute dough evenly around processor blade. Add remaining cup flour and pulse until mixture is evenly distributed around bowl and mass of dough has been broken up, 4 to 6 quick pulses. Empty mixture into medium bowl
- Sprinkle vodka and water over mixture. With rubber spatula, use folding motion to mix, pressing down on dough until dough is slightly tacky and sticks together. Divide dough into two even balls and flatten each into 4-inch disk. Wrap each in plastic wrap and refrigerate at least 45 minutes or up to 2 days.
-
 @ 30ceb64e:7f08bdf5
2024-12-21 17:19:42
@ 30ceb64e:7f08bdf5
2024-12-21 17:19:42I'm prompted to write this after seeing that my part time job offers tuition reimbursement to full time workers, and that I could become a full time worker and get essentially get a full ride to complete my bachelors through flexible and remote courses.
Shoutout to the advice I got from a few Stackers
Just know that degrees dont mean as much as they did in the past. If you invest this time in to school, will it pay off later? It depends on what degree you will be getting, and how quickly you can complete the coursework.
@Satosora
I was in a similar grind a full-time gig and a side hustle while chasing my degree. Ended up specializing in cybersecurity and the degree definitely opened doors I hadn’t even considered. My tip structure is key. Treat your study time like a third job, and don’t skimp on self care. You’ve already got that hustle mindset, so you’re halfway there. Go for it, but keep the balance in check! Good luck!
@Imyourfed
This is how I ended up becoming an economist. I had a couple of jobs, one of which offered tuition benefits, and I took a couple of classes a semester until I finished an econ degree. Then, off to grad school. I say you should do it, as long as you're confident you can handle the workload.
@Undisciplined
Among many others.
Shoutout to the advice I got from a few Nostritches
https://primal.net/e/note166vyza03rwqjq49dez2xktv7vfmq98s8hjf5kjxlcdjg85ffs2mq02243r
https://primal.net/e/note1x93cuy2n90k2y4kms8hn5qwsffcapluw7elxty03jntau75m6rfq094f47
https://primal.net/e/note15z0xfzwm8llqqsgm5aq5j9t0955kt5htzkafhxas93gfd7yn5x2q37dapn
The Nostr freaks were overall against it, while SN freaks were overall for it.
I've reached a dilemma. The dilemma is "why am I doing this?" Are my intentions pure and honorable, or is this fiat credentialism rearing its ugly head. Is this me wanting to better myself and contribute value to the world or is this not staying humble
Am I risking something that I cant see at the moment, should my energy be spent doing other things; starting a business, Freelancing harder, Contributing to open source harder, Spending more time with the wife and kid on the way.
Over the past few years I've become grumbly shouting at friends and family about evil fiat and perfect perfect bitcoin. At what point do I pull a satoshi, and move on to other things. At what point do I take my own advice, realize that I probably have enough bitcoin, and enjoy life.
I'll try to articulate my thoughts the best I can.......although this is a ramble
I want to get a bachelors degree and potentially become a lawyer for the reasons below
-
Stick it to the haters. I naively jumped around telling a few family members what I would do with my life and thought becoming a lawyer wasn't too far fetched. They did, and thought I was crazy and couldn't do it. Fuck em.
-
I have 30 college credits to go towards a bachelors, a lot of time to complete classes, approaching 6 years of experience working at an IP law firm, a rinky dink paralegal certificate, and the possibility to have it all paid for without spending any sats. So the goal seems oddly obtainable.
-
LLM's are great at homework
-
It would make my wife and unborn child more proud of me, which I believe is good.
-
I want to excel in my career and have good job opportunities moving forward. With a bachelors I'd be able to obtain higher paying jobs and have a formidable resume to take advantage of more opportunities as they come by.
-
I have a growing interest in learning this stuff. I think about the samurai wallet boys and keep a side eye on the trial. I'm a sovereign individual thesis guy, and want to see the how the laws will bend to support a new technological paradigm.
-
I read "come and take it" by Cody Wilson and followed a bit of his journey and thought his fight and thoughts on the courts were pretty cool.
In Conclusion, I'm typing these rambling thoughts while working on my part time job, which may become a 2nd full time, because I might head back to school to finish my bachelors, while recognizing that college degrees are mostly scams for suckers.
Kids come out of highschool and are sold the lie that, this is the only path forward. That if you dont go to fancy university than your life is shit. Society looks down upon you with a mocking and judgmental glare. Your parents arent proud of you, and you need to give a very good explanation on why you're throwing your life away. So instead of facing a tidal wave of scrutiny, most kids who can end up going to college and getting into a crazy amount of debt, or dropping out essentially wasting their time while postulating like they were trying to "find themselves". The idea of school in fiat is a rough one anyway, the campuses are communist lgbtq government obediance propaganda training grounds siphoning first principle thinking from its victims with a spooky efficiency.
Ah, wait that was supposed to be a conclusion. Let me try again.
In Conclusion, College degrees are mostly scams for suckers, but maybe armed with better knowledge of what i'm getting into, a bit more focus and more realistic expectations; I can appropriately navigate through the treacherous marshes of keynsian brainwashing into the orange light of sticking it to the man.
originally posted at https://stacker.news/items/819302
-
-
 @ 8fb140b4:f948000c
2023-08-22 12:14:34
@ 8fb140b4:f948000c
2023-08-22 12:14:34As the title states, scratch behind my ear and you get it. 🐶🐾🫡
-
 @ fe32298e:20516265
2024-12-16 20:59:13
@ fe32298e:20516265
2024-12-16 20:59:13Today I learned how to install NVapi to monitor my GPUs in Home Assistant.
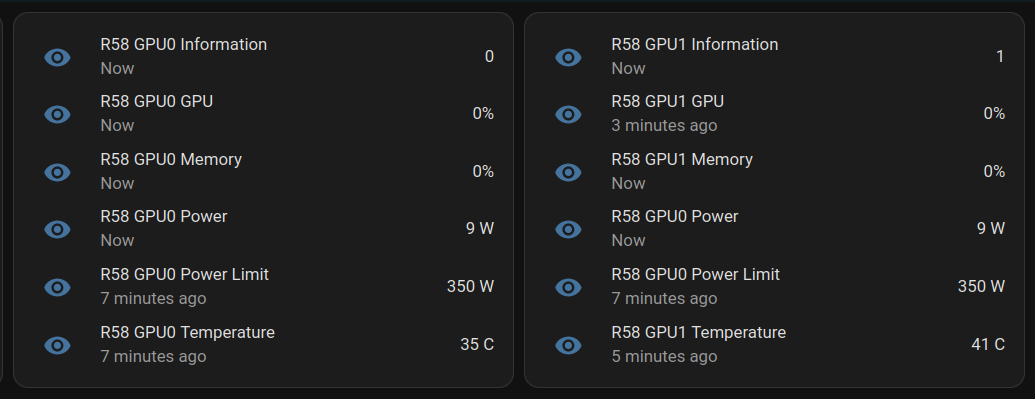
NVApi is a lightweight API designed for monitoring NVIDIA GPU utilization and enabling automated power management. It provides real-time GPU metrics, supports integration with tools like Home Assistant, and offers flexible power management and PCIe link speed management based on workload and thermal conditions.
- GPU Utilization Monitoring: Utilization, memory usage, temperature, fan speed, and power consumption.
- Automated Power Limiting: Adjusts power limits dynamically based on temperature thresholds and total power caps, configurable per GPU or globally.
- Cross-GPU Coordination: Total power budget applies across multiple GPUs in the same system.
- PCIe Link Speed Management: Controls minimum and maximum PCIe link speeds with idle thresholds for power optimization.
- Home Assistant Integration: Uses the built-in RESTful platform and template sensors.
Getting the Data
sudo apt install golang-go git clone https://github.com/sammcj/NVApi.git cd NVapi go run main.go -port 9999 -rate 1 curl http://localhost:9999/gpuResponse for a single GPU:
[ { "index": 0, "name": "NVIDIA GeForce RTX 4090", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 16, "power_limit_watts": 450, "memory_total_gb": 23.99, "memory_used_gb": 0.46, "memory_free_gb": 23.52, "memory_usage_percent": 2, "temperature": 38, "processes": [], "pcie_link_state": "not managed" } ]Response for multiple GPUs:
[ { "index": 0, "name": "NVIDIA GeForce RTX 3090", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 14, "power_limit_watts": 350, "memory_total_gb": 24, "memory_used_gb": 0.43, "memory_free_gb": 23.57, "memory_usage_percent": 2, "temperature": 36, "processes": [], "pcie_link_state": "not managed" }, { "index": 1, "name": "NVIDIA RTX A4000", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 10, "power_limit_watts": 140, "memory_total_gb": 15.99, "memory_used_gb": 0.56, "memory_free_gb": 15.43, "memory_usage_percent": 3, "temperature": 41, "processes": [], "pcie_link_state": "not managed" } ]Start at Boot
Create
/etc/systemd/system/nvapi.service:``` [Unit] Description=Run NVapi After=network.target
[Service] Type=simple Environment="GOPATH=/home/ansible/go" WorkingDirectory=/home/ansible/NVapi ExecStart=/usr/bin/go run main.go -port 9999 -rate 1 Restart=always User=ansible
Environment="GPU_TEMP_CHECK_INTERVAL=5"
Environment="GPU_TOTAL_POWER_CAP=400"
Environment="GPU_0_LOW_TEMP=40"
Environment="GPU_0_MEDIUM_TEMP=70"
Environment="GPU_0_LOW_TEMP_LIMIT=135"
Environment="GPU_0_MEDIUM_TEMP_LIMIT=120"
Environment="GPU_0_HIGH_TEMP_LIMIT=100"
Environment="GPU_1_LOW_TEMP=45"
Environment="GPU_1_MEDIUM_TEMP=75"
Environment="GPU_1_LOW_TEMP_LIMIT=140"
Environment="GPU_1_MEDIUM_TEMP_LIMIT=125"
Environment="GPU_1_HIGH_TEMP_LIMIT=110"
[Install] WantedBy=multi-user.target ```
Home Assistant
Add to Home Assistant
configuration.yamland restart HA (completely).For a single GPU, this works: ``` sensor: - platform: rest name: MYPC GPU Information resource: http://mypc:9999 method: GET headers: Content-Type: application/json value_template: "{{ value_json[0].index }}" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature scan_interval: 1 # seconds
- platform: template sensors: mypc_gpu_0_gpu: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} GPU" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_memory: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Memory" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_power: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Power" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_0_power_limit: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_0_temperature: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Temperature" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'temperature') }}" unit_of_measurement: "°C" ```
For multiple GPUs: ``` rest: scan_interval: 1 resource: http://mypc:9999 sensor: - name: "MYPC GPU0 Information" value_template: "{{ value_json[0].index }}" json_attributes_path: "$.0" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature - name: "MYPC GPU1 Information" value_template: "{{ value_json[1].index }}" json_attributes_path: "$.1" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature
-
platform: template sensors: mypc_gpu_0_gpu: friendly_name: "MYPC GPU0 GPU" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_memory: friendly_name: "MYPC GPU0 Memory" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_power: friendly_name: "MYPC GPU0 Power" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_0_power_limit: friendly_name: "MYPC GPU0 Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_0_temperature: friendly_name: "MYPC GPU0 Temperature" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'temperature') }}" unit_of_measurement: "C"
-
platform: template sensors: mypc_gpu_1_gpu: friendly_name: "MYPC GPU1 GPU" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_1_memory: friendly_name: "MYPC GPU1 Memory" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_1_power: friendly_name: "MYPC GPU1 Power" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_1_power_limit: friendly_name: "MYPC GPU1 Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_1_temperature: friendly_name: "MYPC GPU1 Temperature" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'temperature') }}" unit_of_measurement: "C"
```
Basic entity card:
type: entities entities: - entity: sensor.mypc_gpu_0_gpu secondary_info: last-updated - entity: sensor.mypc_gpu_0_memory secondary_info: last-updated - entity: sensor.mypc_gpu_0_power secondary_info: last-updated - entity: sensor.mypc_gpu_0_power_limit secondary_info: last-updated - entity: sensor.mypc_gpu_0_temperature secondary_info: last-updatedAnsible Role
```
-
name: install go become: true package: name: golang-go state: present
-
name: git clone git: repo: "https://github.com/sammcj/NVApi.git" dest: "/home/ansible/NVapi" update: yes force: true
go run main.go -port 9999 -rate 1
-
name: install systemd service become: true copy: src: nvapi.service dest: /etc/systemd/system/nvapi.service
-
name: Reload systemd daemons, enable, and restart nvapi become: true systemd: name: nvapi daemon_reload: yes enabled: yes state: restarted ```
-
 @ dd664d5e:5633d319
2024-12-07 20:02:01
@ dd664d5e:5633d319
2024-12-07 20:02:01Yeah, so... nah.
People keep trying to explain to me, that women will be better-off, if they become more dangerous. While I can see the inevitableness of women living in remote rural areas learning to shoot with a rifle, and similar, I'm generally against arming women with killing machines.
This is not because I'm averse to the idea of using violence to solve problems (albeit after exhausting better options), or because I don't like guns, or am unfamiliar with them. It's also not because I don't know I would look totally, mind-numbingly hot holding something long and spearlike, while dressed in camo and wearing a T-Shirt that appears to have shrunk in the wash.

It's a more fundamental set of problems, that irks me.
Bazooka Barbie
American gun manufacturers saturated the public and private male market so thoroughly, that they eventually turned to marketing firearms to women.
Men are scary and bad. There is Stranger Danger. We can't just make the neighborhood less dangerous because erm... reasons. Stay safe with a cute gun.

It has gone along with the predictable hypersexualization of the conservative feminine ideal. Since guns are considered aggressive, women with guns are perceived as more sexually available. Guns (and tanks, bombs, bows, etc.) make women "equal", "independent", "feisty", "hot", "freaky", "calculating", "empowered", etc.

Sorta slutty, basically.
This Gun Girl is not like the helpless, hapless, harmless homemaker ideal, of yesteryear. A woman who was dependent, chaste, gentle, wise... and in need of protection. A woman who saw the men around her as people she could rely on for providing her with a safe environment. That woman is au revoir. Now, sistas are doing it for themselves. 💪🏻
The New Martial Missy needs a man, like a fish needs a bicycle... but make it country.
Yeah, it's marketing, but it sure has set the tone, and millions of men have been trained to prefer women who market themselves in this manner. Hard, mean, lean women. That will not remain without wider societal consequences.
You know, I liked that homemaker. I miss her. She's literally me.

Those arms are for cuddling babies, not holding rocket launchers.
Now, that we've all become accustomed to imagery of women holding firearms, it wasn't much of a leap to condition us all to the sight of women in frontline police, guard, or military positions.

Instead of war being a terrible, highly-lethal, territorial fight amongst men, it's now cute, hip, trendy and fun. It's a big party, and women are finally allowed to join in.
Now, women have finally jettisoned the terrible burden of being society's life-bearers and caretakers, and we're just more potential enemy combatants. We know it's okay to punch women, shoot women, etc. since we've been watching it happen on screens, for decades. Women are now often assumed to be fighters, not lovers. Cavalry, not mothers.
Girls on top
Not only does this undermine any female role -- and put female civilians under a cloud of suspicion -- it also reduces mens' claim to be paramount in governance. Why should a man be the Commander in Chief, if women are on the battlefield?
In fact, why should men be in charge of anything, anywhere? Look at them. There they are. Hiding at home. Cowering in their kitchens, wringing their hands and fretting, while courageous, dangerous women protect them from dangers foreign and domestic. Women are the better men, really.
Is this really where we want to go?
The final bitterness
But one thing I find most disturbing is something more personal. The ubiquitous nature of firearms in American homes has made domestic violence increasingly deadly. Adding more guns, for the female residents, often serves to make such violence even more deadly for women.
It turns out, that women are usually reluctant to shoot people they know; even more than men. Women without this inhibition are prone to sharing their home with men missing the same trait. And, now, they have more guns.
-
 @ 04222fa1:634e9de5
2024-12-22 14:05:24
@ 04222fa1:634e9de5
2024-12-22 14:05:24In a room of 100 people
99% are Bitcoiners
How many Bitcoiners need to leave the room, to bring that percentage down to 98%?
originally posted at https://stacker.news/items/820455
-
 @ 20986fb8:cdac21b3
2024-12-18 04:25:48
@ 20986fb8:cdac21b3
2024-12-18 04:25:48ไทย
แนะนำ YakiHonne: เขียนได้ไม่มีขีดจำกัด
YakiHonne คือโปรแกรมแก้ไขข้อความที่ดีที่สุดที่ออกแบบมาเพื่อช่วยให้คุณแสดงออกอย่างสร้างสรรค์ไม่ว่าจะใช้ภาษาใดก็ตาม
ฟีเจอร์ที่คุณจะหลงรัก:
- 🌟 ฟอร์แมตที่หลากหลาย: เพิ่มหัวข้อ, ตัวหนา, ตัวเอียง และอื่นๆ
- 🌏 รองรับหลายภาษา: เขียนได้อย่างราบรื่นทั้งภาษาอังกฤษ, จีน, อาหรับ และญี่ปุ่น
- 🔗 ลิงก์ที่สามารถโต้ตอบได้: เรียนรู้เพิ่มเติมเกี่ยวกับ YakiHonneข้อดี:
1. ใช้งานง่าย
2. เพิ่มความสามารถในการอ่านด้วยสไตล์ที่ปรับแต่งได้
3. รองรับฟอร์แมตที่ซับซ้อนหลายประเภท รวมถึง LateX"YakiHonne คือการเปลี่ยนแปลงที่สำคัญสำหรับผู้สร้างเนื้อหา"
-
 @ 7ed7d5c3:6927e200
2024-12-03 15:46:54
@ 7ed7d5c3:6927e200
2024-12-03 15:46:54Shall I compare thee to a summer’s day? Thou art more lovely and more temperate; Rough winds do shake the darling buds of May, And summer’s lease hath all too short a date;
Sometime too hot the eye of heaven shines,
And often is his gold complexion dimm’d;
And every fair from fair sometime declines,
By chance or nature’s changing course untrimm’d;
``` But thy eternal summer shall not fade Nor lose possession of that fair thou owest; Nor shall Death brag thou wander’st in his shade, When in eternal lines to time thou growest;
So long as men can breathe or eyes can see, So long lives this and this gives life to thee. ```
-
 @ 9f51b59f:75e7c3a2
2024-11-26 20:04:51
@ 9f51b59f:75e7c3a2
2024-11-26 20:04:51Chef's notes
Use bone in or boneless short rib. This recipe also works with ox tail and pork shoulder or any kind of meat that’s ideal for braising low and slow.
Details
- ⏲️ Prep time: 30 mins
- 🍳 Cook time: 2.5-3.5 hours
- 🍽️ Servings: 6-8
Ingredients
- 3 Tablespoons natural cooking oil (I use tallow or ghee)
- 2 lbs boneless short ribs (bone-in also works)
- Salt & Pepper
- 1 small red onion, diced
- 5 garlic cloves rough chopped
- 1 bell or poblano pepper, seeded & diced
- 2 teaspoon chili powder
- 1 teaspoon ancho chili powder
- 1 tablespoon smoked paprika
- 1 tablespoon dark coco powder
- 2 teaspoon cumin
- 1 tablespoon graham masla
- 1 teaspoon dried oregano
- 3 tablespoons apple cider vinegar
- 1/2 cup tomato puree
- 3 tablespoons chipotle adobo sauce
- 3 bay leaves
- 1.5 cups stock or water
- 2 fresh limes, juiced
- Banana leaves, optional
- Avocado, sour cream, lime juice
- Shaved red cabbage with lime juice
Directions
- Preheat oven to 315 degrees F. Using a Dutch oven or braising pan, begin heating oil over high heat on the stove top.
- Season beef with salt and pepper and begin searing in the pot. Once browned on all sides set the beef aside and add the onions, garlic, and peppers to the same pan and reduce the heat.
- Season and cook the veggies 5 to 8 minutes until they start to caramelize. Add the chili pepper, paprika, coco, cumin, marsala, and dried oregano.
- Briefly toast the spices and deglaze with the vinegar and immediately add the tomato puree.
- Add the adobo sauce, broth, and using a stick blender or blender buzz the cooking liquid. (if using banana leaves remove the cooking liquid from the pan or use a new pot with lid. Line the pot with the leaves shingled over one another, return the cooking liquid over the leaves.)
- Return the beef to the pot and cover with lid or foil (fold leaves over the meat then cover).
- Place the pot in the oven and cook for 2 hours before checking, the meat should be fork tender when done.
- Mash the avocado into the sour cream and season with lime juice or hot sauce. Serve on tortillas with the crema and cabbage.
-
 @ e356a30c:11e846f7
2024-12-16 07:26:35
@ e356a30c:11e846f7
2024-12-16 07:26:351. SaaS (Software as a Service) : Delivers software applications over the internet, eliminating the need for local installations.
Real World Examples includes: Google Workspace, Microsoft 365, Salesforce, Dropbox
Key Benefits for Businesses: Reduced IT costs, automatic updates, accessibility from anywhere, scalability, focus on core business
2. PaaS (Platform as a Service): Provides a cloud platform for developing, deploying, and managing applications without the need for building and maintaining the underlying infrastructure.
Real World Examples: Google App Engine, AWS Lambda, Heroku
Key Benefits for Businesses: Faster development and deployment, scalability, reduced infrastructure management, cost-effectiveness
3. **IaaS (Infrastructure as a Service) ** Offers computing resources like servers, storage, and networking on demand.
Real World Examples: Amazon EC2, Microsoft Azure, Google Compute Engine
Benefits for Businesses: Flexibility and control over infrastructure, scalability, cost-efficiency, pay-as-you-go pricing
Reference: * https://techylodge.com/how-does-cloud-computing-work/
-
 @ 9cb3545c:2ff47bca
2024-12-01 00:18:45
@ 9cb3545c:2ff47bca
2024-12-01 00:18:45Hey there! So you’ve got a whopping 50+ Lightning Channels and you’re not keen on them Force Closing? Well, buckle up! This guide will be an additional resource as you navigate through daunting process.
In this post, we will go over some extra tips and tricks not covered in the official guide. While this guide does have some steps that are not covered by Umbrel, its main objective is to provide confidence in the process (not a replacement process), coming from someone who’s been there and done that, and some how came out with all Lightning Channels still running! I highly recommend reading this post fully before starting the migration process.
Before we dive in, here is the Official Guide from the Umbrel team on how to update UmbrelOS from 0.5.4 to 1.x.x. Reference the steps all the time, and follow them carefully.
With that out of the way. Here are some extra TIPs to fill in some gaps I encountered as I went through the process.
The Order of Steps
Tip #1:
In the Official Umbrel Guide, the Umbrel team asks you to start by backing up your data. As a lightning Node Runner, I recommend against this. Because the Bash script will stop all Umbrel Services and your node will remain offline while you prepare a Bootable USB Stick. So definitely don't start with the backup, first get the bootable stick sorted out, then move on to backups.
Creating the Bootable USB Stick
TIP #2:
After many failed attempts to create a bootable USB stick from the link umbrel provides in their official guide. I ended up getting the ISO directly from Umbrels team through their Discord Channel. Unfortunately, I wont be able to share this link here. but just in case the umbrelOS-amd64-usb-installer.iso.xz didnt work for you as well, this could be an alternative route.
TIP #3:
Since Umbrel is an actual full OS now. You might need to handle some BIOS quirks. The umbrelOS Kernal is not signed. So if you have Secure Boot turned on in the BIOS, your PC will try to protect you, and block you from booting into you USB Stick. Turn off Secure Boot and you should be able to bypass this issue. I also had to turn on Legacy Option ROMs as well.
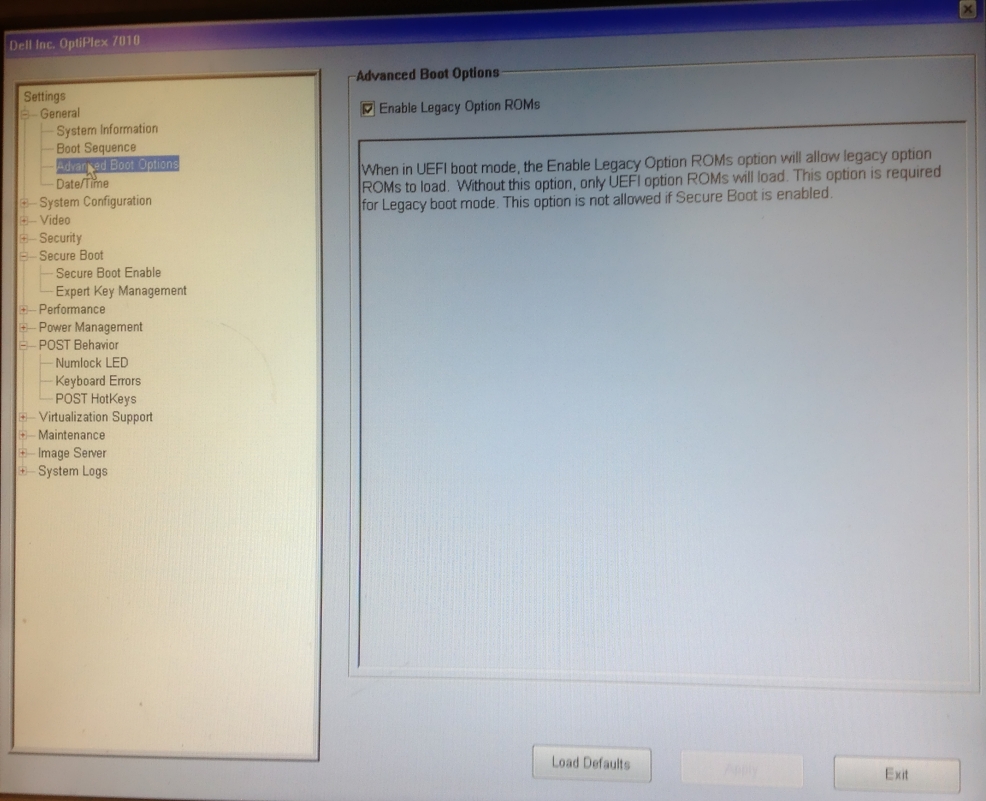
Tip #4:
Test your Bootable USB Stick on a secondary device before you go on trying to update your node. Since turning the node off and on is a hassle, its just easier to be certain the the Bootable Stick is ready before even attempting to upgrade your node.
If all is good, you are ready to get back to the guide and walk through the steps.
Preparing the Hardware
Tip #5:
In the official guide they as you to connect a Keyboard and Screen. This is of course needed. I would highly suggest you connect a mouse as well. My Bios was very stubborn and didn't comply with just a keyboard as I attempted to re-order Boot Sequences.
The Migration Process
Tip #6:
Remember, this is 10 times easier if you are not running a lightning node, but on a lightning node, the Channel.db file is being updated constantly. Once you start the backup process, the script will shutdown umbrel services and start copying. you can''t turn your node back on after this stage. If you do, assume the backup you created through the Bash script is obsolete. and you will have to redo the backup process again. If you really know what you are doing, you probably can surgically copy/paste the LND folder. But its easier not to do this.
But not to worry, if you start the process just keep going (especially if you checked all the TIPs I cover above). I say this out of experience, because after I started the first backup process, it took me about an hour to backup my SSD, but then the Bootable USB stick threw so many errors I gave up, and turned on the node again. Then later re-attempted the process from scratch. This time, since my external SSD was already full, it took 3.5 hours to backup all the files again.
Tip #7:
This will take time, so just trust the migration process and wait for the files to get copied. you are probably copying more than a terabyte worth of data back and forth over USB, Leverage USB 3 if you have it.
Tip #8:
If you have a custom name for your umbrel node. Meaning you do not access it by using umbrel.local, this will be reset to the default umbrel.local after the migration. I am not sure if this could be switched again to a custom name, but for now, this won't cause any issues.
Tip #9:
During the last steps of the Migration process, and once Umbrel has copied the backup back into the SSD, it will finish the process with downloading your apps, and restarting. Don't freak out :D
Tip #10:
I honestly don't have a tenth tip, but thought it would make this list look nicer with one. So my last tip for you is to relax and enjoy the process. And feel free to tag me if you faced any issues. Hopefully it will be something i experienced and will be able to help.
Have Fun, and Good Luck!
-
 @ 2efaa715:3d987331
2024-12-21 16:54:55
@ 2efaa715:3d987331
2024-12-21 16:54:55More than you wanted to know about a little-understood but important aspect of diet and health, explained in a nontechnical manner, with oversimplifications abound.
Your cells need some kind of fuel to function. this fuel can only come (ultimately) from the outside world as food. AKA "diet". your blood carries the fuel to the cells so they can do their work. on most diets, the main fuel for cells is glucose, which the body derives from sugar or carbohydrates (which are basically sugar + some complexity). on other diets, the main fuel for cells is fat. on these diets, fat/lipid particles are carried on little blood ferries called lipoproteins (the final "L" in LDL and HDL). LDL carries lipids to your cells so they can use it, HDL carries unused lipids away from your cells (to the liver) so they can be disposed of. (on both very high carb and very low carb diets, your cells will still use some amount of both glucose and fat for energy, but the ratio will change dramatically).
Naturally, if you have a lot of these ferries in your blood (because you are using fat as cell-fuel), your LDL and HDL counts ("total cholesterol") will be high on basic blood tests.LDL - the ferries that carry fats to your cells to burn - come in two varieties: - small + dense - large + fluffy
both carry fuel to your cells, but the small/dense ones have an unfortunate side-effect of slamming into artery walls, penetrating them, and accidentally depositing their lipids there. This is the "plaque" of cardiovascular disease fame. The large, fluffy particles do not penetrate the arterial walls as readily - they bounce off and keep going on to their destinations. their effect on arterial plaque is not zero, but far less impactful than small, dense particles.In either case, the HDL particles are always good: they remove excess lipids from the body. this is why HDL is "the good cholesterol". There are advanced blood tests available which measure particle size (so, like, an acutally useful test), but odds are your doctor will refuse to order this test. Strange!
We didn't mention Triglycerides yet. Suffice it to say that more triglycerides = smaller, denser LDL particles = more arterial wall penetration = more cardiovascular risk. To finish off our triglycerides sidebar, the dietary patterns that increase triglycerides (bad!) are: excess calories from carbohydrates, added sugars and refined carbohydrates, low fiber intake, low omega-3 intake (especially in combination with excess seed oil intake), high trans fats consumption (more on trans fat in a moment).
Back to finish up cholesterol: this is why a diet that is high in good fats (again, more in a moment) will increase "total cholesterol" - you have more fat boats fueling your cells - but doesn't indicate greater cardiovascular risk: because the large, fluffy particles are not damaging your arteries and the large number of HDL particles are protective!
Furthermore, if you reconsider the sidebar on triglycerides you'll notice that avoiding refined carbohydrates and sugars has the added effect of lowering triglycerides, which keeps the LDL particles even healthier. You'll often see the simple recommendation to keep the HDL/Triglycerides ratio high. this is why. HDL good, triglycerides bad.We didn't even get into insulin sensitivity - one of the most important factors in metabolic health... another time.
A last word on dietary fat types: Not all fats are created equally. You can look into monounsaturated and polyunsaturated on your own, but I want to mention two others here: Trans fat and Saturated fat.
Trans fats mostly come from artificial sources, like processed vegetable or seed oils. most often found in ultra-processed, packaged foods. yuck. trans fat lowers HDL, increases inflammation and increases proportion of small, dense LDL particles. These are all the bad things we discussed above.
Saturated fat is mainly found in meat, dairy and coconut oil. It increases LDL particle size and raises HDL. These are the good things we discussed above.
So, yes, while someone's total cholesterol may go up when eating saturated fats, it doesn't necessarily mean their cardiovascular risk has increased.Now that you understand how cholesterol works, compare moderate saturated fat intake to eating a diet full of refined carbohydrates, sugars, processed vegetable/seed oils, and all the other items we explained above...
Ok really now, the last last word: the "cholesterol" you see on a food label has less impact on blood cholesterol than you thought. the details are too squirrely to go into here, but the takeway is: the fat content discussed above is the lion's share of the impact, with the number you see next to "cholesterol" on your food label having a negligible effect.
diet #paleo #keto #health #healthstr #foodstr #carnivore #cholesterol
-
 @ 4dc2e570:7b8126f9
2024-11-25 17:39:37
@ 4dc2e570:7b8126f9
2024-11-25 17:39:37Chef's notes
Pickled pearl onions can usually be found at a middle eastern grocery store.
Details
- ⏲️ Prep time: 30 - 45 minutes
- 🍳 Cook time: 2 hours and 30 minutes
- 🍽️ Servings: 6
Ingredients
- 2.5 lbs stew meat
- 4 cloves Garlic
- 2 onions
- 6oz Bacon, chopped
- 4 Carrots (cut in 1/2 in pieces)
- 3 celery sticks (cut in 1 in pieces)
- 5 or so small gold potatoes, quartered
- 3ish tbps Flour
- 4 tbsp tomato paste
- 14 oz Guinness Beer
- 3 cups chicken stock
- 1 tsp Thyme
- 2 bay leaves
- Ghee
- Salt and pepper
Directions
- Pat dry then salt and pepper the beef. Melt 1/2 tbsp ghee over high med-high heat. Brown the beef on each side well, makes the stew tasty. This takes patience. Do some breath work while you're at it. :) Add ghee as necessary so browny bits on bottom dont burn. Put meat aside.
- In same pan, sauté onion and garlic for a few min. Throw in bacon till browned. Put in carrot and celery.
- Add 3tbsp flour (or a bit more, basically till oil is soaked up) and stir for a minute. Add tomato paste. Stir a couple more minutes.
- Add thin layer of beer and scrape yummy bits from bottom of pan. Mix everything well. Add rest of beer, broth, and herbs.
- Carmelize the pickled pearl onion on low med heat with a lil olive oil and stirring occasionally.
- Simmer covered for 2 hours. Add potatoes. Simmer for a further 30 minutes uncovered to let the sauce reduce a bit. Salt and pepper as you like. Add in some pearl onions. Enjoy.
-
 @ a012dc82:6458a70d
2024-12-16 04:00:21
@ a012dc82:6458a70d
2024-12-16 04:00:21Table Of Content
-
The Predictable Dance of Bitcoin's Price
-
Economic Cycles and Their Influence on Bitcoin
-
The Role of Bitcoin Halving in These Cycles
-
Echoes of the 2015-2017 Pre-Bull Run Phase
-
A Glimpse into the Future: An Optimistic Outlook with Caveats
-
Conclusion
-
FAQ
In the dynamic world of financial assets, patterns often emerge that hint at the future trajectory of popular investments, especially Bitcoin. A recent deep dive into Bitcoin's behavior suggests that its current price action is reminiscent of its performance between 2015 and 2017. For those who've been tracking its journey, this might evoke a sense of déjà vu. Let's unpack this captivating observation.
The Predictable Dance of Bitcoin's Price
Delphi Digital, a renowned research firm, recently shed light on the intriguing consistency of price trends within the crypto market. Their findings suggest that Bitcoin's current consolidation around the $30,000 mark mirrors its behavior from a few years ago. If history is any guide, we might be gearing up for another all-time high (ATH) for Bitcoin by the end of 2024.
Economic Cycles and Their Influence on Bitcoin:
One cannot discuss Bitcoin's price without considering broader economic trends. Delphi's analysis highlights the cyclical nature of the cryptocurrency market. These cycles, often spanning four years, showcase a pattern: Bitcoin reaches a new ATH, faces a significant drop (often around 80%), bottoms out a year later, and then embarks on a two-year recovery journey. This culminates in another price rally, leading to a fresh ATH.
Interestingly, Bitcoin's price peaks often align with changes in the business cycle, as reflected by the ISM Manufacturing Index. When Bitcoin is at its peak, the ISM shows signs of maxing out, and network activities like transaction volumes reach their zenith. Conversely, when the business cycle signals a rebound, Bitcoin's network activity follows suit.
The Role of Bitcoin Halving in These Cycles:
For those unfamiliar, Bitcoin halving is an event where the reward for mining new blocks is halved, effectively cutting the rate at which new Bitcoins are created. Delphi's report emphasizes the significance of this event in the four-year cycles. Historically, halvings have taken place roughly 18 months after Bitcoin hits its bottom and about seven months before a new ATH. This pattern suggests that the next ATH for Bitcoin could be around the corner, coinciding with the upcoming halving in 2024.
Echoes of the 2015-2017 Pre-Bull Run Phase: The parallels between Bitcoin's current market environment and the 2015-2017 phase are hard to ignore. Both periods exhibit similar market behaviors, economic indicators, and historical trends. The report even notes that trading patterns in broader markets, like the S&P 500, mirror those observed during 2015-2017. Such patterns persisted even during uncertain times, reinforcing the sentiment of that era.
A Glimpse into the Future: An Optimistic Outlook with Caveats:
Delphi's comprehensive analysis paints a hopeful picture for the crypto market. The prediction of a new ATH by the end of 2024, backed by historical halving patterns and economic indicators, strengthens the case for a cycle similar to 2015-2017. The anticipated Bitcoin halving in 2024 further supports the possibility of a bull market by that year's end. However, as with all predictions, there are inherent risks and uncertainties. Yet, the overall sentiment for the crypto market in the upcoming months seems promising, given the historical patterns and current indicators.
Conclusion
For Bitcoin enthusiasts and investors, understanding these patterns and market behaviors can offer valuable insights. While the future remains unpredictable, recognizing these historical parallels can provide a roadmap of sorts. As the saying goes, history often rhymes, and in the case of Bitcoin, it seems to be singing a familiar tune. So, hang tight, folks! The spirit of 2015-2017 might just be making a comeback.
FAQ
What does the recent research by Delphi Digital suggest about Bitcoin's price? The research indicates that Bitcoin's current price action mirrors its behavior between 2015 and 2017, hinting at a potential all-time high by the end of 2024.
How do economic cycles influence Bitcoin's price? Economic cycles, especially as indicated by the ISM Manufacturing Index, often align with Bitcoin's price peaks and network activity.
What is Bitcoin halving, and why is it significant? Bitcoin halving is an event where the reward for mining new blocks is halved. Historically, halvings have been key indicators of upcoming all-time highs for Bitcoin.
Are there similarities between the current market environment and the 2015-2017 phase? Yes, both periods exhibit similar market behaviors, economic indicators, and historical trends, suggesting a potential bull market in the near future.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 8fb140b4:f948000c
2023-07-30 00:35:01
@ 8fb140b4:f948000c
2023-07-30 00:35:01Test Bounty Note