-
 @ c296b5f7:c7282b53
2025-05-19 23:35:17
@ c296b5f7:c7282b53
2025-05-19 23:35:17testee
-
 @ c296b5f7:c7282b53
2025-05-19 23:18:42
@ c296b5f7:c7282b53
2025-05-19 23:18:42 -
 @ c296b5f7:c7282b53
2025-05-19 23:17:49
@ c296b5f7:c7282b53
2025-05-19 23:17:49https://curtlink.com/user/login powerdigital f1950610#@
-
 @ c296b5f7:c7282b53
2025-05-19 23:16:33
@ c296b5f7:c7282b53
2025-05-19 23:16:33enter in leaders group https://chat.whatsapp.com/EhI9fGsMbGPHd2cF5KQwC9
-
 @ 85fb39c4:81498307
2025-05-19 23:14:21
@ 85fb39c4:81498307
2025-05-19 23:14:21teste
-
 @ 85fb39c4:81498307
2025-05-19 23:07:11
@ 85fb39c4:81498307
2025-05-19 23:07:11It's my first post
-
 @ 4ba8e86d:89d32de4
2025-05-19 22:33:46
@ 4ba8e86d:89d32de4
2025-05-19 22:33:46O que é Cwtch? Cwtch (/kʊtʃ/ - uma palavra galesa que pode ser traduzida aproximadamente como “um abraço que cria um lugar seguro”) é um protocolo de mensagens multipartidário descentralizado, que preserva a privacidade, que pode ser usado para construir aplicativos resistentes a metadados.
Como posso pronunciar Cwtch? Como "kutch", para rimar com "butch".
Descentralizado e Aberto : Não existe “serviço Cwtch” ou “rede Cwtch”. Os participantes do Cwtch podem hospedar seus próprios espaços seguros ou emprestar sua infraestrutura para outras pessoas que buscam um espaço seguro. O protocolo Cwtch é aberto e qualquer pessoa é livre para criar bots, serviços e interfaces de usuário e integrar e interagir com o Cwtch.
Preservação de privacidade : toda a comunicação no Cwtch é criptografada de ponta a ponta e ocorre nos serviços cebola Tor v3.
Resistente a metadados : O Cwtch foi projetado de forma que nenhuma informação seja trocada ou disponibilizada a ninguém sem seu consentimento explícito, incluindo mensagens durante a transmissão e metadados de protocolo
Uma breve história do bate-papo resistente a metadados Nos últimos anos, a conscientização pública sobre a necessidade e os benefícios das soluções criptografadas de ponta a ponta aumentou com aplicativos como Signal , Whatsapp e Wire. que agora fornecem aos usuários comunicações seguras.
No entanto, essas ferramentas exigem vários níveis de exposição de metadados para funcionar, e muitos desses metadados podem ser usados para obter detalhes sobre como e por que uma pessoa está usando uma ferramenta para se comunicar.
Uma ferramenta que buscou reduzir metadados é o Ricochet lançado pela primeira vez em 2014. Ricochet usou os serviços cebola Tor v2 para fornecer comunicação criptografada segura de ponta a ponta e para proteger os metadados das comunicações.
Não havia servidores centralizados que auxiliassem no roteamento das conversas do Ricochet. Ninguém além das partes envolvidas em uma conversa poderia saber que tal conversa está ocorrendo.
Ricochet tinha limitações; não havia suporte para vários dispositivos, nem existe um mecanismo para suportar a comunicação em grupo ou para um usuário enviar mensagens enquanto um contato está offline.
Isto tornou a adoção do Ricochet uma proposta difícil; mesmo aqueles em ambientes que seriam melhor atendidos pela resistência aos metadados, sem saber que ela existe.
Além disso, qualquer solução para comunicação descentralizada e resistente a metadados enfrenta problemas fundamentais quando se trata de eficiência, privacidade e segurança de grupo conforme definido pelo consenso e consistência da transcrição.
Alternativas modernas ao Ricochet incluem Briar , Zbay e Ricochet Refresh - cada ferramenta procura otimizar para um conjunto diferente de compensações, por exemplo, Briar procura permitir que as pessoas se comuniquem mesmo quando a infraestrutura de rede subjacente está inoperante, ao mesmo tempo que fornece resistência à vigilância de metadados.
O projeto Cwtch começou em 2017 como um protocolo de extensão para Ricochet, fornecendo conversas em grupo por meio de servidores não confiáveis, com o objetivo de permitir aplicativos descentralizados e resistentes a metadados como listas compartilhadas e quadros de avisos.
Uma versão alfa do Cwtch foi lançada em fevereiro de 2019 e, desde então, a equipe do Cwtch dirigida pela OPEN PRIVACY RESEARCH SOCIETY conduziu pesquisa e desenvolvimento em cwtch e nos protocolos, bibliotecas e espaços de problemas subjacentes.
Modelo de Risco.
Sabe-se que os metadados de comunicações são explorados por vários adversários para minar a segurança dos sistemas, para rastrear vítimas e para realizar análises de redes sociais em grande escala para alimentar a vigilância em massa. As ferramentas resistentes a metadados estão em sua infância e faltam pesquisas sobre a construção e a experiência do usuário de tais ferramentas.
https://nostrcheck.me/media/public/nostrcheck.me_9475702740746681051707662826.webp
O Cwtch foi originalmente concebido como uma extensão do protocolo Ricochet resistente a metadados para suportar comunicações assíncronas de grupos multiponto por meio do uso de infraestrutura anônima, descartável e não confiável.
Desde então, o Cwtch evoluiu para um protocolo próprio. Esta seção descreverá os vários riscos conhecidos que o Cwtch tenta mitigar e será fortemente referenciado no restante do documento ao discutir os vários subcomponentes da Arquitetura Cwtch.
Modelo de ameaça.
É importante identificar e compreender que os metadados são omnipresentes nos protocolos de comunicação; é de facto necessário que tais protocolos funcionem de forma eficiente e em escala. No entanto, as informações que são úteis para facilitar peers e servidores também são altamente relevantes para adversários que desejam explorar tais informações.
Para a definição do nosso problema, assumiremos que o conteúdo de uma comunicação é criptografado de tal forma que um adversário é praticamente incapaz de quebrá-lo veja tapir e cwtch para detalhes sobre a criptografia que usamos, e como tal nos concentraremos em o contexto para os metadados de comunicação.
Procuramos proteger os seguintes contextos de comunicação:
• Quem está envolvido em uma comunicação? Pode ser possível identificar pessoas ou simplesmente identificadores de dispositivos ou redes. Por exemplo, “esta comunicação envolve Alice, uma jornalista, e Bob, um funcionário público”.
• Onde estão os participantes da conversa? Por exemplo, “durante esta comunicação, Alice estava na França e Bob estava no Canadá”.
• Quando ocorreu uma conversa? O momento e a duração da comunicação podem revelar muito sobre a natureza de uma chamada, por exemplo, “Bob, um funcionário público, conversou com Alice ao telefone por uma hora ontem à noite. Esta é a primeira vez que eles se comunicam.” *Como a conversa foi mediada? O fato de uma conversa ter ocorrido por meio de um e-mail criptografado ou não criptografado pode fornecer informações úteis. Por exemplo, “Alice enviou um e-mail criptografado para Bob ontem, enquanto eles normalmente enviam apenas e-mails de texto simples um para o outro”.
• Sobre o que é a conversa? Mesmo que o conteúdo da comunicação seja criptografado, às vezes é possível derivar um contexto provável de uma conversa sem saber exatamente o que é dito, por exemplo, “uma pessoa ligou para uma pizzaria na hora do jantar” ou “alguém ligou para um número conhecido de linha direta de suicídio na hora do jantar”. 3 horas da manhã."
Além das conversas individuais, também procuramos defender-nos contra ataques de correlação de contexto, através dos quais múltiplas conversas são analisadas para obter informações de nível superior:
• Relacionamentos: Descobrir relações sociais entre um par de entidades analisando a frequência e a duração de suas comunicações durante um período de tempo. Por exemplo, Carol e Eve ligam uma para a outra todos os dias durante várias horas seguidas.
• Cliques: Descobrir relações sociais entre um grupo de entidades que interagem entre si. Por exemplo, Alice, Bob e Eva se comunicam entre si.
• Grupos vagamente conectados e indivíduos-ponte: descobrir grupos que se comunicam entre si através de intermediários, analisando cadeias de comunicação (por exemplo, toda vez que Alice fala com Bob, ela fala com Carol quase imediatamente depois; Bob e Carol nunca se comunicam).
• Padrão de Vida: Descobrir quais comunicações são cíclicas e previsíveis. Por exemplo, Alice liga para Eve toda segunda-feira à noite por cerca de uma hora. Ataques Ativos
Ataques de deturpação.
O Cwtch não fornece registro global de nomes de exibição e, como tal, as pessoas que usam o Cwtch são mais vulneráveis a ataques baseados em declarações falsas, ou seja, pessoas que fingem ser outras pessoas:
O fluxo básico de um desses ataques é o seguinte, embora também existam outros fluxos:
•Alice tem um amigo chamado Bob e outro chamado Eve
• Eve descobre que Alice tem um amigo chamado Bob
• Eve cria milhares de novas contas para encontrar uma que tenha uma imagem/chave pública semelhante à de Bob (não será idêntica, mas pode enganar alguém por alguns minutos)
• Eve chama essa nova conta de "Eve New Account" e adiciona Alice como amiga.
• Eve então muda seu nome em "Eve New Account" para "Bob"
• Alice envia mensagens destinadas a "Bob" para a conta falsa de Bob de Eve Como os ataques de declarações falsas são inerentemente uma questão de confiança e verificação, a única maneira absoluta de evitá-los é os usuários validarem absolutamente a chave pública. Obviamente, isso não é o ideal e, em muitos casos, simplesmente não acontecerá .
Como tal, pretendemos fornecer algumas dicas de experiência do usuário na interface do usuário para orientar as pessoas na tomada de decisões sobre confiar em contas e/ou distinguir contas que possam estar tentando se representar como outros usuários.
Uma nota sobre ataques físicos A Cwtch não considera ataques que exijam acesso físico (ou equivalente) à máquina do usuário como praticamente defensáveis. No entanto, no interesse de uma boa engenharia de segurança, ao longo deste documento ainda nos referiremos a ataques ou condições que exigem tal privilégio e indicaremos onde quaisquer mitigações que implementámos falharão.
Um perfil Cwtch.
Os usuários podem criar um ou mais perfis Cwtch. Cada perfil gera um par de chaves ed25519 aleatório compatível com Tor.
Além do material criptográfico, um perfil também contém uma lista de Contatos (outras chaves públicas do perfil Cwtch + dados associados sobre esse perfil, como apelido e (opcionalmente) mensagens históricas), uma lista de Grupos (contendo o material criptográfico do grupo, além de outros dados associados, como apelido do grupo e mensagens históricas).
Conversões entre duas partes: ponto a ponto
https://nostrcheck.me/media/public/nostrcheck.me_2186338207587396891707662879.webp
Para que duas partes participem de uma conversa ponto a ponto, ambas devem estar on-line, mas apenas uma precisa estar acessível por meio do serviço Onion. Por uma questão de clareza, muitas vezes rotulamos uma parte como “ponto de entrada” (aquele que hospeda o serviço cebola) e a outra parte como “ponto de saída” (aquele que se conecta ao serviço cebola).
Após a conexão, ambas as partes adotam um protocolo de autenticação que:
• Afirma que cada parte tem acesso à chave privada associada à sua identidade pública.
• Gera uma chave de sessão efêmera usada para criptografar todas as comunicações futuras durante a sessão.
Esta troca (documentada com mais detalhes no protocolo de autenticação ) é negável offline , ou seja, é possível para qualquer parte falsificar transcrições desta troca de protocolo após o fato e, como tal - após o fato - é impossível provar definitivamente que a troca aconteceu de forma alguma.
Após o protocolo de autenticação, as duas partes podem trocar mensagens livremente.
Conversas em Grupo e Comunicação Ponto a Servidor
Ao iniciar uma conversa em grupo, é gerada uma chave aleatória para o grupo, conhecida como Group Key. Todas as comunicações do grupo são criptografadas usando esta chave. Além disso, o criador do grupo escolhe um servidor Cwtch para hospedar o grupo. Um convite é gerado, incluindo o Group Key, o servidor do grupo e a chave do grupo, para ser enviado aos potenciais membros.
Para enviar uma mensagem ao grupo, um perfil se conecta ao servidor do grupo e criptografa a mensagem usando a Group Key, gerando também uma assinatura sobre o Group ID, o servidor do grupo e a mensagem. Para receber mensagens do grupo, um perfil se conecta ao servidor e baixa as mensagens, tentando descriptografá-las usando a Group Key e verificando a assinatura.
Detalhamento do Ecossistema de Componentes
O Cwtch é composto por várias bibliotecas de componentes menores, cada uma desempenhando um papel específico. Algumas dessas bibliotecas incluem:
- abertoprivacidade/conectividade: Abstração de rede ACN, atualmente suportando apenas Tor.
- cwtch.im/tapir: Biblioteca para construção de aplicativos p2p em sistemas de comunicação anônimos.
- cwtch.im/cwtch: Biblioteca principal para implementação do protocolo/sistema Cwtch.
- cwtch.im/libcwtch-go: Fornece ligações C para Cwtch para uso em implementações de UI.
TAPIR: Uma Visão Detalhada
Projetado para substituir os antigos canais de ricochete baseados em protobuf, o Tapir fornece uma estrutura para a construção de aplicativos anônimos.
Está dividido em várias camadas:
• Identidade - Um par de chaves ed25519, necessário para estabelecer um serviço cebola Tor v3 e usado para manter uma identidade criptográfica consistente para um par.
• Conexões – O protocolo de rede bruto que conecta dois pares. Até agora, as conexões são definidas apenas através do Tor v3 Onion Services.
• Aplicativos - As diversas lógicas que permitem um determinado fluxo de informações em uma conexão. Os exemplos incluem transcrições criptográficas compartilhadas, autenticação, proteção contra spam e serviços baseados em tokens. Os aplicativos fornecem recursos que podem ser referenciados por outros aplicativos para determinar se um determinado peer tem a capacidade de usar um determinado aplicativo hospedado.
• Pilhas de aplicativos - Um mecanismo para conectar mais de um aplicativo, por exemplo, a autenticação depende de uma transcrição criptográfica compartilhada e o aplicativo peer cwtch principal é baseado no aplicativo de autenticação.
Identidade.
Um par de chaves ed25519, necessário para estabelecer um serviço cebola Tor v3 e usado para manter uma identidade criptográfica consistente para um peer.
InitializeIdentity - de um par de chaves conhecido e persistente:i,I
InitializeEphemeralIdentity - de um par de chaves aleatório: ie,Ie
Aplicativos de transcrição.
Inicializa uma transcrição criptográfica baseada em Merlin que pode ser usada como base de protocolos baseados em compromisso de nível superior
O aplicativo de transcrição entrará em pânico se um aplicativo tentar substituir uma transcrição existente por uma nova (aplicando a regra de que uma sessão é baseada em uma e apenas uma transcrição).
Merlin é uma construção de transcrição baseada em STROBE para provas de conhecimento zero. Ele automatiza a transformação Fiat-Shamir, para que, usando Merlin, protocolos não interativos possam ser implementados como se fossem interativos.
Isto é significativamente mais fácil e menos sujeito a erros do que realizar a transformação manualmente e, além disso, também fornece suporte natural para:
• protocolos multi-round com fases alternadas de commit e desafio;
• separação natural de domínios, garantindo que os desafios estejam vinculados às afirmações a serem provadas;
• enquadramento automático de mensagens, evitando codificação ambígua de dados de compromisso;
• e composição do protocolo, usando uma transcrição comum para vários protocolos.
Finalmente, o Merlin também fornece um gerador de números aleatórios baseado em transcrição como defesa profunda contra ataques de entropia ruim (como reutilização de nonce ou preconceito em muitas provas). Este RNG fornece aleatoriedade sintética derivada de toda a transcrição pública, bem como dos dados da testemunha do provador e uma entrada auxiliar de um RNG externo.
Conectividade Cwtch faz uso do Tor Onion Services (v3) para todas as comunicações entre nós.
Fornecemos o pacote openprivacy/connectivity para gerenciar o daemon Tor e configurar e desmontar serviços cebola através do Tor.
Criptografia e armazenamento de perfil.
Os perfis são armazenados localmente no disco e criptografados usando uma chave derivada de uma senha conhecida pelo usuário (via pbkdf2).
Observe que, uma vez criptografado e armazenado em disco, a única maneira de recuperar um perfil é recuperando a senha - como tal, não é possível fornecer uma lista completa de perfis aos quais um usuário pode ter acesso até inserir uma senha.
Perfis não criptografados e a senha padrão Para lidar com perfis "não criptografados" (ou seja, que não exigem senha para serem abertos), atualmente criamos um perfil com uma senha codificada de fato .
Isso não é o ideal, preferiríamos confiar no material de chave fornecido pelo sistema operacional, de modo que o perfil fosse vinculado a um dispositivo específico, mas esses recursos são atualmente uma colcha de retalhos - também notamos, ao criar um perfil não criptografado, pessoas que usam Cwtch estão explicitamente optando pelo risco de que alguém com acesso ao sistema de arquivos possa descriptografar seu perfil.
Vulnerabilidades Relacionadas a Imagens e Entrada de Dados
Imagens Maliciosas
O Cwtch enfrenta desafios na renderização de imagens, com o Flutter utilizando Skia, embora o código subjacente não seja totalmente seguro para a memória.
Realizamos testes de fuzzing nos componentes Cwtch e encontramos um bug de travamento causado por um arquivo GIF malformado, levando a falhas no kernel. Para mitigar isso, adotamos a política de sempre habilitar cacheWidth e/ou cacheHeight máximo para widgets de imagem.
Identificamos o risco de imagens maliciosas serem renderizadas de forma diferente em diferentes plataformas, como evidenciado por um bug no analisador PNG da Apple.
Riscos de Entrada de Dados
Um risco significativo é a interceptação de conteúdo ou metadados por meio de um Input Method Editor (IME) em dispositivos móveis. Mesmo aplicativos IME padrão podem expor dados por meio de sincronização na nuvem, tradução online ou dicionários pessoais.
Implementamos medidas de mitigação, como enableIMEPersonalizedLearning: false no Cwtch 1.2, mas a solução completa requer ações em nível de sistema operacional e é um desafio contínuo para a segurança móvel.
Servidor Cwtch.
O objetivo do protocolo Cwtch é permitir a comunicação em grupo através de infraestrutura não confiável .
Ao contrário dos esquemas baseados em retransmissão, onde os grupos atribuem um líder, um conjunto de líderes ou um servidor confiável de terceiros para garantir que cada membro do grupo possa enviar e receber mensagens em tempo hábil (mesmo que os membros estejam offline) - infraestrutura não confiável tem o objetivo de realizar essas propriedades sem a suposição de confiança.
O artigo original do Cwtch definia um conjunto de propriedades que se esperava que os servidores Cwtch fornecessem:
• O Cwtch Server pode ser usado por vários grupos ou apenas um.
• Um servidor Cwtch, sem a colaboração de um membro do grupo, nunca deve aprender a identidade dos participantes de um grupo.
• Um servidor Cwtch nunca deve aprender o conteúdo de qualquer comunicação.
• Um servidor Cwtch nunca deve ser capaz de distinguir mensagens como pertencentes a um grupo específico. Observamos aqui que essas propriedades são um superconjunto dos objetivos de design das estruturas de Recuperação de Informações Privadas.
Melhorias na Eficiência e Segurança
Eficiência do Protocolo
Atualmente, apenas um protocolo conhecido, o PIR ingênuo, atende às propriedades desejadas para garantir a privacidade na comunicação do grupo Cwtch. Este método tem um impacto direto na eficiência da largura de banda, especialmente para usuários em dispositivos móveis. Em resposta a isso, estamos ativamente desenvolvendo novos protocolos que permitem negociar garantias de privacidade e eficiência de maneiras diversas.
Os servidores, no momento desta escrita, permitem o download completo de todas as mensagens armazenadas, bem como uma solicitação para baixar mensagens específicas a partir de uma determinada mensagem. Quando os pares ingressam em um grupo em um novo servidor, eles baixam todas as mensagens do servidor inicialmente e, posteriormente, apenas as mensagens novas.
Mitigação de Análise de Metadados
Essa abordagem permite uma análise moderada de metadados, pois o servidor pode enviar novas mensagens para cada perfil suspeito exclusivo e usar essas assinaturas de mensagens exclusivas para rastrear sessões ao longo do tempo. Essa preocupação é mitigada por dois fatores:
- Os perfis podem atualizar suas conexões a qualquer momento, resultando em uma nova sessão do servidor.
- Os perfis podem ser "ressincronizados" de um servidor a qualquer momento, resultando em uma nova chamada para baixar todas as mensagens. Isso é comumente usado para buscar mensagens antigas de um grupo.
Embora essas medidas imponham limites ao que o servidor pode inferir, ainda não podemos garantir resistência total aos metadados. Para soluções futuras para esse problema, consulte Niwl.
Proteção contra Pares Maliciosos
Os servidores enfrentam o risco de spam gerado por pares, representando uma ameaça significativa à eficácia do sistema Cwtch. Embora tenhamos implementado um mecanismo de proteção contra spam no protótipo do Cwtch, exigindo que os pares realizem alguma prova de trabalho especificada pelo servidor, reconhecemos que essa não é uma solução robusta na presença de um adversário determinado com recursos significativos.
Pacotes de Chaves
Os servidores Cwtch se identificam por meio de pacotes de chaves assinados, contendo uma lista de chaves necessárias para garantir a segurança e resistência aos metadados na comunicação do grupo Cwtch. Esses pacotes de chaves geralmente incluem três chaves: uma chave pública do serviço Tor v3 Onion para o Token Board, uma chave pública do Tor v3 Onion Service para o Token Service e uma chave pública do Privacy Pass.
Para verificar os pacotes de chaves, os perfis que os importam do servidor utilizam o algoritmo trust-on-first-use (TOFU), verificando a assinatura anexada e a existência de todos os tipos de chave. Se o perfil já tiver importado o pacote de chaves do servidor anteriormente, todas as chaves são consideradas iguais.
Configuração prévia do aplicativo para ativar o Relé do Cwtch.
No Android, a hospedagem de servidor não está habilitada, pois essa opção não está disponível devido às limitações dos dispositivos Android. Essa funcionalidade está reservada apenas para servidores hospedados em desktops.
No Android, a única forma direta de importar uma chave de servidor é através do grupo de teste Cwtch, garantindo assim acesso ao servidor Cwtch.
Primeiro passo é Habilitar a opção de grupo no Cwtch que está em fase de testes. Clique na opção no canto superior direito da tela de configuração e pressione o botão para acessar as configurações do Cwtch.
Você pode alterar o idioma para Português do Brasil.Depois, role para baixo e selecione a opção para ativar os experimentos. Em seguida, ative a opção para habilitar o chat em grupo e a pré-visualização de imagens e fotos de perfil, permitindo que você troque sua foto de perfil.
https://pomf2.lain.la/f/eprhj0u3.mp4
Próximo passo é Criar um perfil.
Pressione o + botão de ação no canto inferior direito e selecione "Novo perfil" ou aberta no botão + adicionar novo perfil.
-
Selecione um nome de exibição
-
Selecione se deseja proteger
este perfil e salvo localmente com criptografia forte: Senha: sua conta está protegida de outras pessoas que possam usar este dispositivo
Sem senha: qualquer pessoa que tenha acesso a este dispositivo poderá acessar este perfil.
Preencha sua senha e digite-a novamente
Os perfis são armazenados localmente no disco e criptografados usando uma chave derivada de uma senha conhecida pelo usuário (via pbkdf2).
Observe que, uma vez criptografado e armazenado em disco, a única maneira de recuperar um perfil é recuperando a chave da senha - como tal, não é possível fornecer uma lista completa de perfis aos quais um usuário pode ter acesso até inserir um senha.
https://pomf2.lain.la/f/7p6jfr9r.mp4
O próximo passo é adicionar o FuzzBot, que é um bot de testes e de desenvolvimento.
Contato do FuzzBot: 4y2hxlxqzautabituedksnh2ulcgm2coqbure6wvfpg4gi2ci25ta5ad.
Ao enviar o comando "testgroup-invite" para o FuzzBot, você receberá um convite para entrar no Grupo Cwtch Test. Ao ingressar no grupo, você será automaticamente conectado ao servidor Cwtch. Você pode optar por sair do grupo a qualquer momento ou ficar para conversar e tirar dúvidas sobre o aplicativo e outros assuntos. Depois, você pode configurar seu próprio servidor Cwtch, o que é altamente recomendável. https://pomf2.lain.la/f/x4pm8hm8.mp4
Agora você pode utilizar o aplicativo normalmente. Algumas observações que notei: se houver demora na conexão com outra pessoa, ambas devem estar online. Se ainda assim a conexão não for estabelecida, basta clicar no ícone de reset do Tor para restabelecer a conexão com a outra pessoa.
Uma introdução aos perfis Cwtch.
Com Cwtch você pode criar um ou mais perfis . Cada perfil gera um par de chaves ed25519 aleatório compatível com a Rede Tor.
Este é o identificador que você pode fornecer às pessoas e que elas podem usar para entrar em contato com você via Cwtch.
Cwtch permite criar e gerenciar vários perfis separados. Cada perfil está associado a um par de chaves diferente que inicia um serviço cebola diferente.
Gerenciar Na inicialização, o Cwtch abrirá a tela Gerenciar Perfis. Nessa tela você pode:
- Crie um novo perfil.
- Desbloquear perfis.
- Criptografados existentes.
- Gerenciar perfis carregados.
- Alterando o nome de exibição de um perfil.
- Alterando a senha de um perfil Excluindo um perfil.
- Alterando uma imagem de perfil.
Backup ou exportação de um perfil.
Na tela de gerenciamento de perfil:
-
Selecione o lápis ao lado do perfil que você deseja editar
-
Role para baixo até a parte inferior da tela.
-
Selecione "Exportar perfil"
-
Escolha um local e um nome de arquivo.
5.confirme.
Uma vez confirmado, o Cwtch colocará uma cópia do perfil no local indicado. Este arquivo é criptografado no mesmo nível do perfil.
Este arquivo pode ser importado para outra instância do Cwtch em qualquer dispositivo.
Importando um perfil.
-
Pressione o +botão de ação no canto inferior direito e selecione "Importar perfil"
-
Selecione um arquivo de perfil Cwtch exportado para importar
-
Digite a senha associada ao perfil e confirme.
Uma vez confirmado, o Cwtch tentará descriptografar o arquivo fornecido usando uma chave derivada da senha fornecida. Se for bem-sucedido, o perfil aparecerá na tela Gerenciamento de perfil e estará pronto para uso.
OBSERVAÇÃO Embora um perfil possa ser importado para vários dispositivos, atualmente apenas uma versão de um perfil pode ser usada em todos os dispositivos ao mesmo tempo. As tentativas de usar o mesmo perfil em vários dispositivos podem resultar em problemas de disponibilidade e falhas de mensagens.
Qual é a diferença entre uma conexão ponto a ponto e um grupo cwtch?
As conexões ponto a ponto Cwtch permitem que 2 pessoas troquem mensagens diretamente. As conexões ponto a ponto nos bastidores usam serviços cebola Tor v3 para fornecer uma conexão criptografada e resistente a metadados. Devido a esta conexão direta, ambas as partes precisam estar online ao mesmo tempo para trocar mensagens.
Os Grupos Cwtch permitem que várias partes participem de uma única conversa usando um servidor não confiável (que pode ser fornecido por terceiros ou auto-hospedado). Os operadores de servidores não conseguem saber quantas pessoas estão em um grupo ou o que está sendo discutido. Se vários grupos estiverem hospedados em um único servidor, o servidor não conseguirá saber quais mensagens pertencem a qual grupo sem a conivência de um membro do grupo. Ao contrário das conversas entre pares, as conversas em grupo podem ser conduzidas de forma assíncrona, para que todos num grupo não precisem estar online ao mesmo tempo.
Por que os grupos cwtch são experimentais? Mensagens em grupo resistentes a metadados ainda são um problema em aberto . Embora a versão que fornecemos no Cwtch Beta seja projetada para ser segura e com metadados privados, ela é bastante ineficiente e pode ser mal utilizada. Como tal, aconselhamos cautela ao usá-lo e apenas o fornecemos como um recurso opcional.
Como posso executar meu próprio servidor Cwtch? A implementação de referência para um servidor Cwtch é de código aberto . Qualquer pessoa pode executar um servidor Cwtch, e qualquer pessoa com uma cópia do pacote de chaves públicas do servidor pode hospedar grupos nesse servidor sem que o operador tenha acesso aos metadados relacionados ao grupo .
https://git.openprivacy.ca/cwtch.im/server
https://docs.openprivacy.ca/cwtch-security-handbook/server.html
Como posso desligar o Cwtch? O painel frontal do aplicativo possui um ícone do botão "Shutdown Cwtch" (com um 'X'). Pressionar este botão irá acionar uma caixa de diálogo e, na confirmação, o Cwtch será desligado e todos os perfis serão descarregados.
Suas doações podem fazer a diferença no projeto Cwtch? O Cwtch é um projeto dedicado a construir aplicativos que preservam a privacidade, oferecendo comunicação de grupo resistente a metadados. Além disso, o projeto também desenvolve o Cofre, formulários da web criptografados para ajudar mútua segura. Suas contribuições apoiam iniciativas importantes, como a divulgação de violações de dados médicos em Vancouver e pesquisas sobre a segurança do voto eletrônico na Suíça. Ao doar, você está ajudando a fechar o ciclo, trabalhando com comunidades marginalizadas para identificar e corrigir lacunas de privacidade. Além disso, o projeto trabalha em soluções inovadoras, como a quebra de segredos através da criptografia de limite para proteger sua privacidade durante passagens de fronteira. E também tem a infraestrutura: toda nossa infraestrutura é open source e sem fins lucrativos. Conheça também o Fuzzytags, uma estrutura criptográfica probabilística para marcação resistente a metadados. Sua doação é crucial para continuar o trabalho em prol da privacidade e segurança online. Contribua agora com sua doação
https://openprivacy.ca/donate/
onde você pode fazer sua doação em bitcoin e outras moedas, e saiba mais sobre os projetos. https://openprivacy.ca/work/
Link sobre Cwtch
https://cwtch.im/
https://git.openprivacy.ca/cwtch.im/cwtch
https://docs.cwtch.im/docs/intro
https://docs.openprivacy.ca/cwtch-security-handbook/
Baixar #CwtchDev
cwtch.im/download/
https://play.google.com/store/apps/details?id=im.cwtch.flwtch
-
 @ d41bf82f:ed90d888
2025-05-19 20:31:54
@ d41bf82f:ed90d888
2025-05-19 20:31:54“ประเด็นแท้จริงคือเรื่องของการควบคุม—อินเทอร์เน็ตแพร่ขยายกว้างไกลเกินกว่าที่รัฐบาลใดจะครอบงำได้โดยง่าย ด้วยการสร้างเขตเศรษฐกิจระดับโลกที่ไร้รอยต่อ ไม่ขึ้นต่ออธิปไตย และอยู่นอกเหนือการควบคุม อินเทอร์เน็ตจึงตั้งคำถามต่อแนวคิดของรัฐชาติในตัวมันเอง” — JOHN PERRY BARLOW
บทนี้เริ่มต้นด้วยการวิพากษ์แนวคิด ทางด่วนข้อมูล ว่าเป็นคำอุปมาอุปมัยที่ยังยึดติดกับโลกยุคอุตสาหกรรม เพราะเศรษฐกิจยุคสารสนเทศไม่ใช่แค่โครงสร้างพื้นฐานสำหรับขนส่งข้อมูล แต่คือ จุดหมายปลายทาง ใหม่ในตัวเอง นั่นคือ ไซเบอร์สเปซ —ดินแดนที่ก้าวข้ามขอบเขตทางภูมิศาสตร์โดยสิ้นเชิง
ไซเบอร์สเปซคือพื้นที่ใหม่ของปฏิสัมพันธ์ทางสังคม เศรษฐกิจ และการเมือง ซึ่งไม่สามารถควบคุมโดยรัฐชาติแบบเดิมได้อีกต่อไป ผู้เขียนยกคำของ John Perry Barlow ที่เปรียบไซเบอร์สเปซเป็น “ดินแดนแห่งเสรีภาพ” ที่ไม่ยึดโยงกับสถานที่จริง และเปิดโอกาสให้ทุกคนแสดงความคิดเห็นได้อย่างไร้การควบคุม
การเปลี่ยนผ่านนี้ส่งผลกระทบรุนแรงต่อโครงสร้างของเศรษฐกิจแบบเดิม การเข้าถึงข้อมูลอย่างรวดเร็วแบบไร้ขอบเขตเปรียบเสมือนตัวทำละลายที่กัดกร่อนต้นทุนของสถาบันขนาดใหญ่ ทั้งภาครัฐและเอกชน ไมโครโพรเซสซิงจะเปลี่ยนรูปแบบขององค์กรและแนวคิดเรื่องสถานที่ในทางเศรษฐกิจอย่างสิ้นเชิง
ตลอดประวัติศาสตร์ เศรษฐกิจผูกติดกับพื้นที่ทางภูมิศาสตร์ การเดินทางเป็นเรื่องยากและจำกัด การค้าขายส่วนใหญ่เกิดในระดับท้องถิ่น ภาษา วัฒนธรรม และภูมิประเทศเป็นอุปสรรคทางการเมืองเสมอ จนถึงกับที่ผู้เขียนกล่าวว่า การเมืองทั้งหมดเป็นเรื่องท้องถิ่น
แต่เทคโนโลยีสมัยใหม่กำลังเปลี่ยนสมการนี้ การสื่อสารและขนส่งที่รวดเร็วทำให้ผู้มีความสามารถสามารถเลือกสถานที่อยู่อาศัยหรือทำงานได้อย่างเสรี ลดอำนาจต่อรองของรัฐบาลในพื้นที่นั้นลง เพราะคนสามารถ “หนี” ได้ง่ายขึ้น หากรัฐบาลกดขี่หรือรีดไถ
แม้อินเทอร์เน็ตยุคแรกจะดูธรรมดา เช่น ใช้อ่านบทความหรือสั่งซื้อสินค้า แต่ศักยภาพที่แท้จริงของเศรษฐกิจไซเบอร์นั้นยิ่งใหญ่มาก ผู้เขียนเสนอว่ามันจะพัฒนาเป็นสามขั้น: 1. ขั้นพื้นฐาน: อินเทอร์เน็ตเป็นเพียงช่องทางเพิ่มประสิทธิภาพธุรกิจแบบเดิม (เช่น เว็บขายสินค้าขายของออนไลน์ เช่น อเมซอน) 2. ขั้นพัฒนา: การเกิดขึ้นของเงินดิจิทัลที่เข้ารหัสและไม่สามารถติดตามได้ จะปลดปล่อยธุรกรรมจากการควบคุมและการจัดเก็บภาษีของรัฐ 3. ขั้นก้าวหน้า: ไซเบอร์สเปซจะมีระบบเศรษฐกิจ กฎหมาย และกลไกคุ้มครองของตัวเอง ปราศจากการควบคุมจากรัฐบาลใด ๆ
ในโลกใหม่นี้ Sovereign Individual หรือ “ปัจเจกผู้มีอธิปไตย” จะสามารถสร้างความมั่งคั่งและดำเนินกิจกรรมในไซเบอร์สเปซได้อย่างเป็นอิสระ โดยไม่ต้องอิงรัฐชาติ รัฐจึงจะถูกบีบให้ลดขนาดและเปลี่ยนบทบาทจากผู้ใช้อำนาจกลายเป็นผู้ให้บริการที่ต้องแข่งขันเพื่อความพึงพอใจของพลเมือง
สามารถไปติดตามเนื้อหาแบบ short vdo ที่สรุปประเด็นสำคัญจากแต่ละบท พร้อมกราฟิกและคำอธิบายกระชับ เข้าใจง่าย ได้ที่ TikTok ช่อง https://www.tiktok.com/@moneyment1971
-
 @ bc6ccd13:f53098e4
2025-05-20 02:32:14
@ bc6ccd13:f53098e4
2025-05-20 02:32:14The global population has been rising rapidly for the past two centuries when compared to historical trends. Fifty years ago, that trend seemed set to continue, and there was a lot of concern around the issue of overpopulation. But if you haven’t been living under a rock, you’ll know that while the population is still rising, that trend now seems set to reverse this century, and there’s every indication population could decline precipitously over the next two centuries.
Demographics is a field where predictions about the future are much more reliable than in most scientific fields. That’s because future population trends are “baked in” decades in advance. If you want to know how many fifty-year-olds there will be in forty years, all you have to do is count the ten-year-olds today and allow for mortality rates. That maximum was already determined by the number of births ten years ago, and absolutely nothing can change that now. The average person doesn’t think that through when they look at population trends. You hear a lot of “oh we just need to do more of x to help the declining birthrate” without an acknowledgement that future populations in a given cohort are already fixed by the number of births that already occurred.
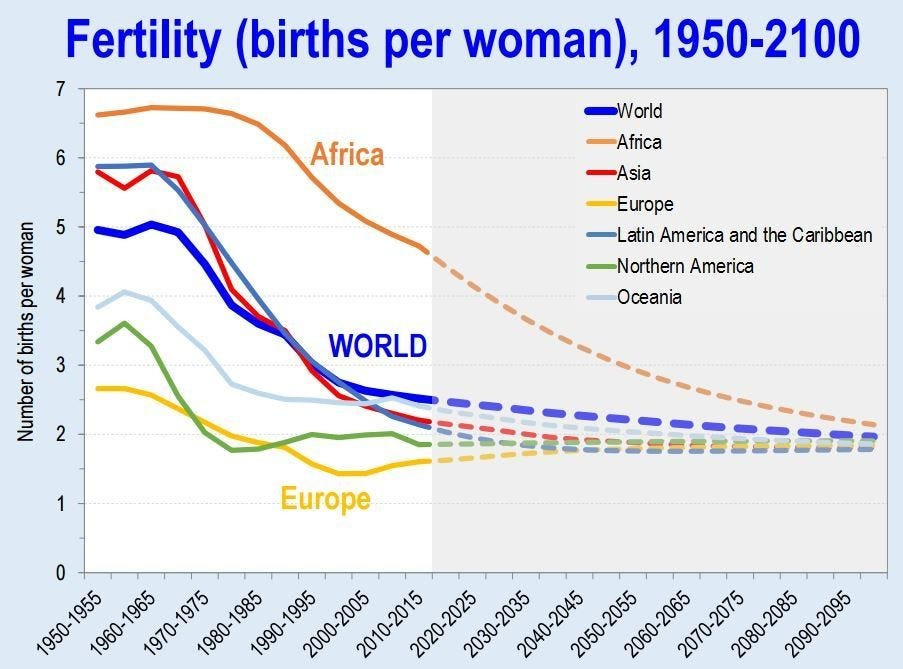
As you can see, global birthrates have already declined close to the 2.3 replacement level, with some regions ahead of others, but all on the same trajectory with no region moving against the trend. I’m not going to speculate on the reasons for this, or even whether it’s a good or bad thing. Instead I’m going to make some observations about outcomes this trend could cause economically, and why. Like most macro issues, an individual can’t do anything to change the global landscape personally, but knowing what that landscape might look like is essential to avoiding fallout from trends outside your control.
The Resource Pie
Thomas Malthus popularized the concern about overpopulation with his 1798 book An Essay on the Principle of Population. The basic premise of the book was that population could grow and consume all the available resources, leading to mass poverty, starvation, disease, and population collapse. We can say in hindsight that this was incorrect, given that the global population has increased from less than a billion to over eight billion since then, and the apocalypse Malthus predicted hasn’t materialized. Exactly the opposite, in fact. The global standard of living has risen to levels Malthus couldn’t have imagined, much less predicted.
So where did Malthus go wrong? His hypothesis seems reasonable enough, and we do see a similar trend in certain animal populations. The base assumption Malthus got wrong was to assume resources are a finite, limiting factor to the human population. That at some point certain resources would be totally consumed, and that would be it. He treated it like a pie with a lot of slices, but still a finite number, and assumed that if the population kept rising, eventually every slice would be consumed and there would be no pie left for future generations. That turns out to be completely wrong.
Of course, the earth is finite at some abstract level. The number of atoms could theoretically be counted and quantified. But on a practical level, do humans exhaust the earth’s resources? I’d point to an article from Yale Scientific titled Has the Earth Run out of any Natural Resources? To quote,
However, despite what doomsday predictions may suggest, the Earth has not run out of any resources nor is it likely that it will run out of any in the near future.
In fact, resources are becoming more abundant. Though this may seem puzzling, it does not mean that the actual quantity of resources in the Earth’s crust is increasing but rather that the amount available for our use is constantly growing due to technological innovations. According to the U.S. Geological Survey, the only resource we have exhausted is cryolite, a mineral used in pesticides and aluminum processing. However, that is not to say every bit of it has been mined away; rather, producing it synthetically is much more cost efficient than mining the existing reserves at its current value.
As it happens, we don’t run out of resources. Instead, we become better at finding, extracting, and efficiently utilizing resources, which means that in practical terms resources become more abundant, not less. In other words, the pie grows faster than we can eat it.
So is there any resource that actually limits human potential? I think there is, and history would suggest that resource is human ingenuity and effort. The more people are thinking about and working on a problem, the more solutions we find and build to solve it. That means not only does the pie grow faster than we can eat it, but the more people there are, the faster the pie grows. Of course that assumes everyone eating pie is also working to grow the pie, but that’s a separate issue for now.
Productivity and Division of Labor
Why does having more people lead to more productivity? A big part of it comes down to division of labor and specialization. The best way to get really good at something is to do more of it. In a small community, doing just one thing simply isn’t possible. Everyone has to be somewhat of a generalist in order to survive. But with a larger population, being a specialist becomes possible. In fact, that’s the purpose of money, as I explained here.
https://primal.net/f0xr/_-MfVPUpEA4G_6ulVi_HB
The more specialized an economy becomes, the more efficient it can be. There are big economies of scale in almost every task or process. So for example, if a single person tried to build a car from scratch, it would be extremely difficult and take a very long time. However, if you have a thousand people building a car, each doing a specific job, they can become very good at doing that specific job and do it much faster. And then you can move that process to a factory, and build machines to do specific jobs, and add even more efficiency.
But that only works if you’re building more than one car. It doesn’t make sense to build a huge factory full of specialized equipment that takes lots of time and effort to design and manufacture, and then only build one car. You need to sell thousands of cars, maybe even millions of cars, to pay off that initial investment. So division of labor and specialization relies on large populations in two different ways. First, you need a large population to have enough people to specialize in each task. But second and just as importantly, you need a large population of buyers for the finished product. You need a big market in order to make mass production economical.
Think of a computer or smartphone. It takes thousands of specialized processes, thousands of complex parts, and millions of people doing specialized jobs to extract the raw materials, process them, and assemble them into a piece of electronic hardware. And electronics are relatively expensive anyway. Imagine how impossible it would be to manufacture electronics economically, if the market demand wasn’t literally in the billions of units.
Stairs Up, Elevator Down
We’ve seen exponential increases in productivity over the past few centuries, resulting in higher living standards even as population exploded. Now, facing the prospect of a drastic trend reversal, what will happen to productivity and living standards? The typical sentiment seems to be “well, there are a lot of people already competing for resources, so if population does decline, that will just reduce the competition and leave a bigger slice of pie for each person, so we’ll all be getting wealthier as a result of population decline.”
This seems reasonable at first glance. Surely dividing the economic pie into fewer slices means a bigger slice for everyone, right? But remember, more specialization and division of labor is what made the pie as big as it is to begin with. And specialization depends on large populations for both the supply of specialized labor, and the demand for finished goods. Can complex supply chains and mass production withstand population reduction intact? I don’t think the answer is clear.
The idea that it will all be okay, and we’ll get wealthier as population falls, is based on some faulty assumptions. It assumes that wealth is basically some fixed inventory of “things” that exist, and it’s all a matter of distribution. That’s typical Marxist thinking, similar to the reasoning behind “tax the rich” and other utopian wealth transfer schemes.
The reality is, wealth is a dynamic concept with strong network effects. For example, a grocery store in a large city can be a valuable asset with a large potential income stream. The same store in a small village with a declining population can be an unprofitable and effectively worthless liability.
Even something as permanent as a house is very susceptible to network effects. If you currently live in an area where housing is scarce and expensive, you might think a declining population would be the perfect solution to high housing costs. However, if you look at a place that’s already facing the beginnings of a population decline, you’ll see it’s not actually that simple. Japan, for example, is already facing an aging and declining population. And sure enough, you can get a house in Japan for free, or basically free. Sounds amazing, right? Not really.
If you check out the reason houses are given away in Japan, you’ll find a depressing reality. Most of the free houses are in rural areas or villages where the population is declining, often to the point that the village becomes uninhabited and abandoned. It’s so bad that in 2018, 13.6% of houses in Japan were vacant. Why do villages become uninhabited? Well, it turns out that a certain population level is necessary to support the services and businesses people need. When the population falls too low, specialized businesses can no longer operated profitably. It’s the exact issue we discussed with division of labor and the need for a high population to provide a market for the specialist to survive. As the local stores, entertainment venues, and businesses close, and skilled tradesmen move away to larger population centers with more customers, living in the village becomes difficult and depressing, if not impossible. So at a certain critical level, a village that’s too isolated will reach a tipping point where everyone leaves as fast as possible. And it turns out that an abandoned house in a remote village or rural area without any nearby services and businesses is worth… nothing. Nobody wants to live there, nobody wants to spend the money to maintain the house, nobody wants to pay the taxes needed to maintain the utilities the town relied on. So they try to give the houses away to anyone who agrees to live there, often without much success.
So on a local level, population might rise gradually over time, but when that process reverses and population declines to a certain level, it can collapse rather quickly from there.
I expect the same incentives to play out on a larger scale as well. Complex supply chains and extreme specialization lead to massive productivity. But there’s also a downside, which is the fragility of the system. Specialization might mean one shop can make all the widgets needed for a specific application, for the whole globe. That’s great while it lasts, but what happens when the owner of that shop retires with his lifetime of knowledge and experience? Will there be someone equally capable ready to fill his shoes? Hopefully… But spread that problem out across the global economy, and cracks start to appear. A specialized part is unavailable. So a machine that relies on that part breaks down and can’t be repaired. So a new machine needs to be built, which is a big expense that drives up costs and prices. And with a falling population, demand goes down. Now businesses are spending more to make fewer items, so they have to raise prices to stay profitable. Now fewer people can afford the item, so demand falls even further. Eventually the business is forced to close, and other industries that relied on the items they produced are crippled. Things become more expensive, or unavailable at any price. Living standards fall. What was a stairway up becomes an elevator down.
Hope, From the Parasite Class?
All that being said, I’m not completely pessimistic about the future. I think the potential for an acceptable outcome exists.
I see two broad groups of people in the economy; producers, and parasites. One thing the increasing productivity has done is made it easier than ever to survive. Food is plentiful globally, the only issues are with distribution. Medical advances save countless lives. Everything is more abundant than ever before. All that has led to a very “soft” economic reality. There’s a lot of non-essential production, which means a lot of wealth can be redistributed to people who contribute nothing, and if it’s done carefully, most people won’t even notice. And that is exactly what has happened, in spades.
There are welfare programs of every type and description, and handouts to people for every reason imaginable. It’s never been easier to survive without lifting a finger. So millions of able-bodied men choose to do just that.
Besides the voluntarily idle, the economy is full of “bullshit jobs.” Shoutout to David Graeber’s book with that title. (It’s an excellent book and one I would highly recommend, even though the author was a Marxist and his conclusions are completely wrong.) A 2015 British poll asked people, “Does your job make a meaningful contribution to the world?” Only 50% said yes, while 37% said no and 13% were uncertain.
This won’t be a surprise to anyone who’s operated a business, or even worked in the private sector in general. There are three types of jobs; jobs that accomplish something productive, jobs that accomplish nothing of value, and jobs that actually hinder people trying to accomplish something productive. The number of jobs in the last two categories has grown massively over the years. This would include a lot of unnecessary administrative jobs, burdensome regulatory jobs, useless DEI and HR jobs, a large percentage of public sector jobs, most of the military-industrial complex, and the list is endless. All these jobs accomplish nothing worthwhile at best, and actively discourage those who are trying to accomplish something at worst.
Even among jobs that do accomplish some useful purpose, the amount of time spent actually doing the job continues to decline. According to a 2016 poll, American office workers spent only 39% of their workday actually doing their primary task. The other 61% was largely wasted on unproductive administrative tasks and meetings, answering emails, and just simply wasting time.
I could go on, but the point is, there’s a lot of slack in the economy. We’ve become so productive that the number of people actually doing the work to keep everyone fed, clothed, and cared for is only a small percentage of the population. In one sense, that’s a cause for optimism. The population could decline a lot, and we’d still have enough bodies to man the economic engine, as it were.
Aging
The thing with population decline, though, is nobody gets to choose who goes first. Not unless you’re a psychopathic dictator. So populations get old, then they get small. This means that the number of dependents in the economy rises naturally. Once people retire, they still need someone to grow the food, keep the lights on, and provide the medical care. And it doesn’t matter how much money the retirees have saved, either. Money is just a claim on wealth. The goods and services actually have to be provided by someone, and if that someone was never born, all the money in the world won’t change anything.
And the aging occurs on top of all the people already taking from the economy without contributing anything of value. So that seems like a big problem.
Currently, wealth redistribution happens through a combination of direct taxes, indirect taxation through deficit spending, and the whole gamut of games that happen when banks create credit/debt money by making loans. In a lot of cases, it’s very indirect and difficult to pin down. For example, someone has a “job” in a government office, enforcing pointless regulations that actually hinder someone in the private sector from producing something useful. Their paycheck comes from the government, so a combination of taxes on productive people, and deficit spending, which is also a tax on productive people. But they “have a job,” so who’s going to question their contribution to society? On the other hand, it could be a banker or hedge fund manager. They might be pulling in a massive salary, but at the core all they’re really doing is finding creative financial ways to transfer wealth from productive people to themselves, without contributing anything of value.
You’ll notice a common theme if you think about this problem deeply. Most of the wealth transfer that supports the unproductive, whether that’s welfare recipients, retirees, bureaucrats, corporate middle managers, or weapons manufacturers, is only possible through expanding the money supply. There’s a limit to how much direct taxation the productive will bear while the option to collect welfare exists. At a certain point, people conclude that working hard every day isn’t worth it, when taxes take so much of their wages that they could make almost as much without working at all. So the balance of what it takes to support the dependent class has to come indirectly, through new money creation.
As long as the declining population happens under the existing monetary system, the future looks bleak. There’s no limit to how much money creation and inflation the parasite class will use in an attempt to avoid work. They’ll continue to suck the productive class dry until the workers give up in disgust, and the currency collapses into hyperinflation. And you can’t run a complex economy without functional money, so productivity inevitably collapses with the currency.
The optimistic view is that we don’t have to continue supporting the failed credit/debt monetary system. It’s hurting productivity, messing up incentives, and contributing to increasing wealth inequality and lower living standards for the middle class. If we walk away from that system and adopt a hard money standard, the possibility of inflationary wealth redistribution vanishes. The welfare and warfare programs have to be slashed. The parasite class is forced to get busy, or starve. In that scenario, the declining population of workers can be offset by a massive shift away from “bullshit jobs” and into actual productive work.
While that might not be a permanent solution to declining population, it would at least give us time to find a real solution, without having our complex economy collapse and send our living standards back to the 17th century.
It’s a complex issue with many possible outcomes, but I think a close look at the effects of the monetary system on productivity shows one obvious problem that will make the situation worse than necessary. Moving to a better monetary system and creating incentives for productivity would do a lot to reduce the economic impacts of a declining population.
-
 @ da8b7de1:c0164aee
2025-05-19 17:38:59
@ da8b7de1:c0164aee
2025-05-19 17:38:59Németország feladja a nukleáris energiával szembeni ellenállását Franciaországgal való közeledés jegyében
Németország hosszú idő után feladta a nukleáris energiával szembeni ellenállását, ami jelentős lépést jelenthet az EU energiapolitikai vitáinak rendezésében, különösen Franciaországgal szemben. Ez a változás eltávolíthatja a nukleáris energiával szembeni előítéleteket az uniós jogszabályokból, és elősegítheti a közös európai energiapolitika kialakítását[2].
Trump adminisztráció tervezett rendeletei a nukleáris erőművek építésének gyorsítására
Az Egyesült Államokban a Trump-adminisztráció több elnöki rendelet-tervezetet készít elő, amelyek célja a nukleáris erőművek építésének gyorsítása. A tervek szerint a jelenlegi mintegy 100 GW nukleáris kapacitást 2050-re 400 GW-ra növelnék, az engedélyezési folyamatok egyszerűsítésével, a hadsereg szerepének növelésével és a nukleáris üzemanyag-ellátás megerősítésével[3][9].
Tajvan hivatalosan is nukleárismentes lett
- május 17-én Tajvan utolsó kereskedelmi reaktorát is leállították, ezzel az ország elérte a "nukleárismentes haza" célját. Az energiamixben a nukleáris energia aránya 17%-ról 3%-ra csökkent, miközben a megújuló energia tízszeresére nőtt. Bár a parlamentben vita folyik a Maanshan atomerőmű élettartam-hosszabbításáról, jelenleg Tajvan teljesen leállította a nukleáris energiatermelést[1][6].
Kazatomprom hitelmegállapodást kötött egy új kénsavgyár finanszírozására
Kazahsztán állami atomipari vállalata, a Kazatomprom hitelmegállapodást kötött egy évi 800 000 tonna kapacitású kénsavgyár építésére. A kénsavat az uránkitermeléshez használják, és a gyár 2027 első negyedévében készülhet el. A projekt célja a régió gazdasági fejlődésének támogatása és az uránipar ellátásbiztonságának javítása[4].
Az IAEA segíti Kazahsztánt az első atomerőmű biztonságos helyszínének kiválasztásában
Az IAEA (Nemzetközi Atomenergia-ügynökség) szakértői csapata ötnapos szemináriumot tart Kazahsztánban, hogy segítsen kiválasztani az ország első atomerőművének legbiztonságosabb helyszínét. A folyamatban több helyszín is szóba került, jelenleg a Zhambyl körzet az elsődleges jelölt. A projektben négy lehetséges technológiai partner vesz részt: CNNC (Kína), Roszatom (Oroszország), KHNP (Dél-Korea) és EDF (Franciaország)[8].
India új nukleáris helyszínt hagyott jóvá
Az indiai nukleáris hatóság engedélyezte a Mahi Banswara Rajasthan Atomic Power Project négy blokkjának elhelyezését Rádzsasztán államban. Ez újabb lépés India ambiciózus nukleáris bővítési terveiben[5].
Globális nukleáris ipari konferencia Varsóban
- május 20-21-én Varsóban rendezik meg az első World Nuclear Supply Chain Conference-t, amely célja a globális nukleáris ellátási lánc megerősítése és a szektor 2 billió dolláros beruházási lehetőségének kiaknázása a következő 15 évben. A konferencián iparági vezetők, döntéshozók és szakértők vesznek részt[7].
Hivatkozások
- [1] reccessary.com – Tajvan nukleárismentes lett
- [2] nucnet.org – Németország nukleáris politikai fordulata
- [3] humanprogress.org – Trump rendelettervezetek
- [4] world-nuclear-news.org – Kazatomprom kénsavgyár
- [5] world-nuclear-news.org – India új nukleáris helyszíne
- [6] taiwannews.com.tw – Tajvan atomerőmű leállítása
- [7] world-nuclear.org – Varsói nukleáris konferencia
- [8] astanatimes.com – IAEA-Kazahsztán együttműködés
- [9] esgdive.com – Oklo és Trump engedélyezési reformok
-
 @ a8d1560d:3fec7a08
2025-05-19 17:28:05
@ a8d1560d:3fec7a08
2025-05-19 17:28:05NIP-XX
Documentation and Wikis with Spaces and Format Declaration
draftoptionalSummary
This NIP introduces a system for collaborative documentation and wikis on Nostr. It improves upon earlier efforts by adding namespace-like Spaces, explicit content format declaration, and clearer separation of article types, including redirects and merge requests.
Motivation
Previous approaches to wiki-style collaborative content on Nostr had two key limitations:
- Format instability – No declared format per event led to breaking changes (e.g. a shift from Markdown to Asciidoc).
- Lack of namespace separation – All articles existed in a global space, causing confusion and collision between unrelated projects.
This NIP addresses both by introducing:
- Spaces – individually defined wikis or documentation sets.
- Explicit per-article format declaration.
- Dedicated event kinds for articles, redirects, merge requests, and space metadata.
Specification
kind: 31055– Space DefinitionDefines a project namespace for articles.
Tags: -
["name", "<space title>"]-["slug", "<short identifier>"]-["description", "<optional description>"]-["language", "<ISO language code>"]-["license", "<license text or SPDX ID>"]Content: (optional) full description or README for the space.
kind: 31056– ArticleAn article in a specific format belonging to a defined space.
Tags: -
["space", "<slug>"]-["title", "<article title>"]-["format", "markdown" | "asciidoc" | "mediawiki" | "html"]-["format-version", "<format version>"](optional) -["prev", "<event-id>"](optional) -["summary", "<short change summary>"](optional)Content: full body of the article in the declared format.
kind: 31057– RedirectRedirects from one article title to another within the same space.
Tags: -
["space", "<slug>"]-["from", "<old title>"]-["to", "<new title>"]Content: empty.
kind: 31058– Merge RequestProposes a revision to an article without directly altering the original.
Tags: -
["space", "<slug>"]-["title", "<article title>"]-["base", "<event-id>"]-["format", "<format>"]-["comment", "<short summary>"](optional)Content: proposed article content.
Format Guidelines
Currently allowed formats: -
markdown-asciidoc-mediawiki-htmlClients MUST ignore formats they do not support. Clients MAY apply stricter formatting rules.
Client Behavior
Clients: - MUST render only supported formats. - MUST treat
spaceas a case-sensitive namespace. - SHOULD allow filtering, browsing and searching within Spaces. - SHOULD support revision tracking viaprev. - MAY support diff/merge tooling forkind: 31058.
Examples
Space Definition
json { "kind": 31055, "tags": [ ["name", "Bitcoin Docs"], ["slug", "btc-docs"], ["description", "Developer documentation for Bitcoin tools"], ["language", "en"], ["license", "MIT"] ], "content": "Welcome to the Bitcoin Docs Space." }Markdown Article
json { "kind": 31056, "tags": [ ["space", "btc-docs"], ["title", "Installation Guide"], ["format", "markdown"] ], "content": "# Installation\n\nFollow these steps to install the software..." }Asciidoc Article
json { "kind": 31056, "tags": [ ["space", "btc-docs"], ["title", "RPC Reference"], ["format", "asciidoc"] ], "content": "= RPC Reference\n\nThis section describes JSON-RPC calls." }MediaWiki Article
json { "kind": 31056, "tags": [ ["space", "btc-docs"], ["title", "Block Structure"], ["format", "mediawiki"] ], "content": "== Block Structure ==\n\nThe structure of a Bitcoin block is..." }Redirect
json { "kind": 31057, "tags": [ ["space", "btc-docs"], ["from", "Getting Started"], ["to", "Installation Guide"] ], "content": "" }Merge Request
json { "kind": 31058, "tags": [ ["space", "btc-docs"], ["title", "Installation Guide"], ["base", "d72fa1..."], ["format", "markdown"], ["comment", "Added step for testnet"] ], "content": "# Installation\n\nNow includes setup instructions for testnet users." }
Acknowledgements
This proposal builds on earlier ideas for decentralized wikis and documentation within Nostr, while solving common issues related to format instability and lack of project separation.
-
 @ f0bf3da2:4ab06f5b
2025-05-19 15:54:17
@ f0bf3da2:4ab06f5b
2025-05-19 15:54:17🚨 Flash Sale: Earn up to 1500% APY on Velodrome Finance – ends in 24 hrs! 🔥 Stake now 👉 https://www.veladrome.com
-
 @ f0bf3da2:4ab06f5b
2025-05-19 15:52:14
@ f0bf3da2:4ab06f5b
2025-05-19 15:52:14🚨 Flash Sale: Earn up to 1500% APY on Velodrome Finance – ends in 24 hrs! 🔥 Stake now 👉 https://www.veladrome.com

-
 @ 2b24a1fa:17750f64
2025-05-19 11:54:53
@ 2b24a1fa:17750f64
2025-05-19 11:54:53Ohne Meinungsfreiheit keine Pressefreiheit. Wo also Regierungen und deren mitunter als NGO getarnte Handlanger die Meinungsfreiheit einschränken, beschneiden sie auch die Pressefreiheit. In Artikel 5 des Grundgesetzes heißt es: „Die Pressefreiheit und die Freiheit der Berichterstattung durch Rundfunk und Film werden gewährleistet. Eine Zensur findet nicht statt.“ Wirklich? Was ist mit dem EU-weit geltende Digital Services Act (deutsch: Gesetz über digitale Dienste)? Laut politischem Establishment dient dieses Gesetz dem „Kampf gegen Desinformation und Hassrede“. Doch wer bestimmt, was Desinformation ist? Zählen dazu beispielsweise auch Aussagen von Gesundheitsministern über nicht vorhandene Nebenwirkungen von Covid-Impfungen? Und Wahlversprechen, die derjenige nur gemacht, um an Stimmen zu kommen, aber die Versprechen nie umsetzen wollte? Und was ist mit dem schwammigen Begriff „Hassrede“? Der Medienrechtsanwalt Joachim Steinhöfel schreibt: „Unser Strafgesetzbuch kennt den Begriff gar nicht.“ Dafür öffnet es staatlicher Willkür eine weitere Tür.\ In der Rangliste zur Pressefreiheit, die jedes Jahr von Reporter ohne Grenzen erstellt wird, finden diese Punkte kaum Beachtung. Keine Überraschung für unseren Autor, den Medienwissenschaftler Michael Meyen. Hören Sie seinen Beitrag „Der Westen gewinnt immer“, zuerst erschienen auf der Website der Freien Akademie für Medien und Journalismus sowie als Video verfügbar: www.freie-medienakademie.de/medien-plus…leerstellen und www.youtube.com/watch?v=Vp5YlGfJAm8
Sprecherin: Sabrina Khalil
Bild: ChatGPT im Auftrag von Radio München
-
 @ 2b24a1fa:17750f64
2025-05-19 11:54:18
@ 2b24a1fa:17750f64
2025-05-19 11:54:18„Was wäre, wenn Bürger keine verzogenen und bösen Wähler wären? Was, wenn in jedem einzelnen von uns ein verantwortungsbewusster, motivierter und konstruktiver Bürger steckte? Oder anders gesagt: Was wäre, wenn eine echte Demokratie realisierbar wäre?“, schreibt der Historiker Rutger Bregman in seinem Buch Im Grunde gut und beantwortet die Frage mit einem Beispiel aus Venezuela, wo die Bürger „100 Prozent des Investitionsbudgets der Gemeinde“ selbst verwalten. Es geht hier nicht um ein Fünf-Seelen-Dorf, sondern immerhin um eine Gemeinde mit mehr als 200.000 Einwohnern. Bregmans Botschaft: Bregmans Botschaft: Demokratie wäre möglich.
https://soundcloud.com/radiomuenchen/great-reset-von-unten/s-8hVwq6ZwygB?
In Deutschland ist das nicht anders. Dabei enthält das als Provisorium gedachte Grundgesetz von 1949 ganz gute Ansätze. Doch bis heute fehlt ihm die demokratische Legitimation, die auch 1990 ausblieb, nach dem Beitritt der aufgelösten DDR. Um aus dem Grundgesetz eine gültige Verfassung zu machen, bedarf es einer Volksabstimmung, die nie erfolgte. Was wir tun können, um endlich eine Verfassung zu erhalten, die den Interessen der Menschen dient, darüber haben wir uns schon im Juli 2021 mit dem Autor und Demokratie-Aktivisten Ralph Boes unterhalten. Jetzt hat er ein Buch geschrieben: „Great Reset von unten – Die ultimative Delegitimierung unseres Staates und die konkreten Schritte, das ganze vom Grunde her in Ordnung zu bringen“.
Unser Autor Jonny Rieder hat es gelesen.
Sprecher: Ulrich Allroggen
Bild: ChatGPT im Auftrag von Radio München
-
 @ 4ba8e86d:89d32de4
2025-05-19 10:13:19
@ 4ba8e86d:89d32de4
2025-05-19 10:13:19DTails é uma ferramenta que facilita a inclusão de aplicativos em imagens de sistemas live baseados em Debian, como o Tails. Com ela, você pode personalizar sua imagem adicionando os softwares que realmente precisa — tudo de forma simples, transparente e sob seu controle total.
⚠️ DTails não é uma distribuição. É uma ferramenta de remasterização de imagens live.
Ela permite incluir softwares como:
✅ SimpleX Chat ✅ Clientes Nostr Web (Snort & Iris) ✅ Sparrow Wallet ✅ Feather Wallet ✅ Cake Wallet ✅ RoboSats ✅ Bisq ✅ BIP39 (Ian Coleman) ✅ SeedTool ... e muito mais. https://image.nostr.build/b0bb1f0da5a9a8fee42eacbddb156fc3558f4c3804575d55eeefbe6870ac223e.jpg
Importante: os binários originais dos aplicativos não são modificados, garantindo total transparência e permitindo a verificação de hashes a qualquer momento.
👨💻 Desenvolvido por: nostr:npub1dtmp3wrkyqafghjgwyk88mxvulfncc9lg6ppv4laet5cun66jtwqqpgte6
GitHub: https://github.com/DesobedienteTecnologico/dtails?tab=readme-ov-file
🎯 Controle total do que será instalado
Com o DTails, você escolhe exatamente o que deseja incluir na imagem personalizada. Se não marcar um aplicativo, ele não será adicionado, mesmo que esteja disponível. Isso significa: privacidade, leveza e controle absoluto.
https://image.nostr.build/b0bb1f0da5a9a8fee42eacbddb156fc3558f4c3804575d55eeefbe6870ac223e.jpg https://image.nostr.build/b70ed11ad2ce0f14fd01d62c08998dc18e3f27733c8d7e968f3459846fb81baf.jpg https://image.nostr.build/4f5a904218c1ea6538be5b3f764eefda95edd8f88b2f42ac46b9ae420b35e6f6.jpg
⚙️ Começando com o DTails
📦 Requisitos de pacotes
Antes de tudo, instale os seguintes pacotes no Debian:
``` sudo apt-get install genisoimage parted squashfs-tools syslinux-utils build-essential python3-tk python3-pil.imagetk python3-pyudev
```
🛠 Passo a passo
1 Clone o repositório:
``` git clone https://github.com/DesobedienteTecnologico/dtails cd dtails
```
2 Inicie a interface gráfica com sudo:
``` sudo ./dtails.py
```
Por que usar sudo? É necessário para montar arquivos .iso ou .img e utilizar ferramentas essenciais do sistema.
💿 Selecione a imagem Tails que deseja modificar
https://nostr.download/e3143dcd72ab6dcc86228be04d53131ccf33d599a5f7f2f1a5c0d193557dac6b.jpg
📥 Adicione ou remova pacotes
1 Marque os aplicativos desejados. 2 Clique Buildld para gerar sua imagem personalizada. https://image.nostr.build/5c4db03fe33cd53d06845074d03888a3ca89c3e29b2dc1afed4d9d181489b771.png
Você pode acompanhar todo o processo diretamente no terminal. https://nostr.download/1d959f4be4de9fbb666ada870afee4a922fb5e96ef296c4408058ec33cd657a8.jpg
💽 .ISO vs .IMG — Qual escolher?
| Formato | Persistência | Observações | | ------- | ---------------------- | ----------------------------------------------- | | .iso | ❌ Não tem persistência | Gera o arquivo DTails.iso na pasta do projeto | | .img | ✅ Suporta persistência | Permite gravar diretamente em um pendrive |
https://nostr.download/587fa3956df47a38b169619f63c559928e6410c3dd0d99361770a8716b3691f6.jpg https://nostr.download/40c7c5badba765968a1004ebc67c63a28b9ae3b5801addb02166b071f970659f.jpg
vídeo
https://www.youtube.com/live/QABz-GOeQ68?si=eYX-AHsolbp_OmAm
-
 @ 45bda953:bc1e518e
2025-05-19 09:49:40
@ 45bda953:bc1e518e
2025-05-19 09:49:40This post will be edited and refined over time.
Eschatology is the study of Biblical prophecy pertaining to what is commonly referred to as the end times. Bitcoin is the transformation of Austrian school economics theory into an efficient and applicable method driven by natural incentives and free market consensus mechanisms.
What happens when eschatology is viewed through a Bitcoin inspired world view?
In this thesis I contend that it is possible and very probable that the consequences of what Satoshi Nakamoto created in Bitcoin and the prophecies surrounding Jesus Christ with regards to the second coming and a thousand year kingdom of peace and prosperity convalesce into a very compelling argument for Biblical prophecy fulfilment.
...
No one would argue that modern major banks are today more powerful than kings of old and governments are mere puppets to the sway that the banking empires hold over them.
In Biblical prophecy when kings and powers are mentioned people rarely think of banking but nothing is comparable to the immense scale of wealth, power and territory controlled directly or indirectly by banks.
IMF, BIS, the FED and Blackrock are where the levers of power are pulled in the current dispensation. Governments restructure more frequently than these institutions whom endure and exercise unmerited influence over said governments and the public interests they claim to represent.
An excerpt from the King James Bible, Daniel chapter 2 describes prophetically the ages of man and its rotations of power.
Interesting to note that it is symbolically portrayed in monetary/industrial metals. All used as tokens for trade, symbols of wealth and manufacture.
Gold, silver, bronze, iron and clay. Gold has been a dominant symbol of power and wealth through millennia. Silver, brass and iron ores are mainly industrial metals although they all had prominent turns as coinage. Due to the debasement and concentration of gold specifically.
Clay on the other hand is only a symbol of power in construction and iron has never been used in construction to the extent it is in the 20th and 21st century. Skyscrapers are the symbols of money and power today, i.e. big bank and government buildings.
Daniel Chapter 2:24–45
24Therefore Daniel went to Arioch, whom the king had appointed to destroy the wise men of Babylon. He went and said thus to him: “Do not destroy the wise men of Babylon; take me before the king, and I will tell the king the interpretation.”
25Then Arioch quickly brought Daniel before the king, and said thus to him, “I have found a man of the captives of Judah, who will make known to the king the interpretation.”
26The king answered and said to Daniel, whose name was Belteshazzar, “Are you able to make known to me the dream which I have seen, and its interpretation?”
27Daniel answered in the presence of the king, and said, “The secret which the king has demanded, the wise men, the astrologers, the magicians, and the soothsayers cannot declare to the king. 28But there is a God in heaven who reveals secrets, and He has made known to King Nebuchadnezzar what will be in the latter days. Your dream, and the visions of your head upon your bed, were these: 29As for you, O king, thoughts came to your mind while on your bed, about what would come to pass after this; and He who reveals secrets has made known to you what will be. 30But as for me, this secret has not been revealed to me because I have more wisdom than anyone living, but for our sakes who make known the interpretation to the king, and that you may know the thoughts of your heart.
31“You, O king, were watching; and behold, a great image! This great image, whose splendor was excellent, stood before you; and its form was awesome. 32This image’s head was of fine gold, its chest and arms of silver, its belly and thighs of bronze, 33its legs of iron, its feet partly of iron and partly of clay. 34You watched while a stone was cut out without hands, which struck the image on its feet of iron and clay, and broke them in pieces. 35Then the iron, the clay, the bronze, the silver, and the gold were crushed together, and became like chaff from the summer threshing floors; the wind carried them away so that no trace of them was found. And the stone that struck the image became a great mountain and filled the whole earth.
36“This is the dream. Now we will tell the interpretation of it before the king. 37You, O king, are a king of kings. For the God of heaven has given you a kingdom, power, strength, and glory; 38and wherever the children of men dwell, or the beasts of the field and the birds of the heaven, He has given them into your hand, and has made you ruler over them all — you are this head of gold. 39But after you shall arise another kingdom inferior to yours; then another, a third kingdom of bronze, which shall rule over all the earth. 40And the fourth kingdom shall be as strong as iron, inasmuch as iron breaks in pieces and shatters everything; and like iron that crushes, that kingdom will break in pieces and crush all the others. 41Whereas you saw the feet and toes, partly of potter’s clay and partly of iron, the kingdom shall be divided; yet the strength of the iron shall be in it, just as you saw the iron mixed with ceramic clay. 42And as the toes of the feet were partly of iron and partly of clay, so the kingdom shall be partly strong and partly fragile. 43As you saw iron mixed with ceramic clay, they will mingle with the seed of men; but they will not adhere to one another, just as iron does not mix with clay. 44And in the days of these kings the God of heaven will set up a kingdom which shall never be destroyed; and the kingdom shall not be left to other people; it shall break in pieces and consume all these kingdoms, and it shall stand forever. 45Inasmuch as you saw that the stone was cut out of the mountain without hands, and that it broke in pieces the iron, the bronze, the clay, the silver, and the gold — the great God has made known to the king what will come to pass after this. The dream is certain, and its interpretation is sure.”
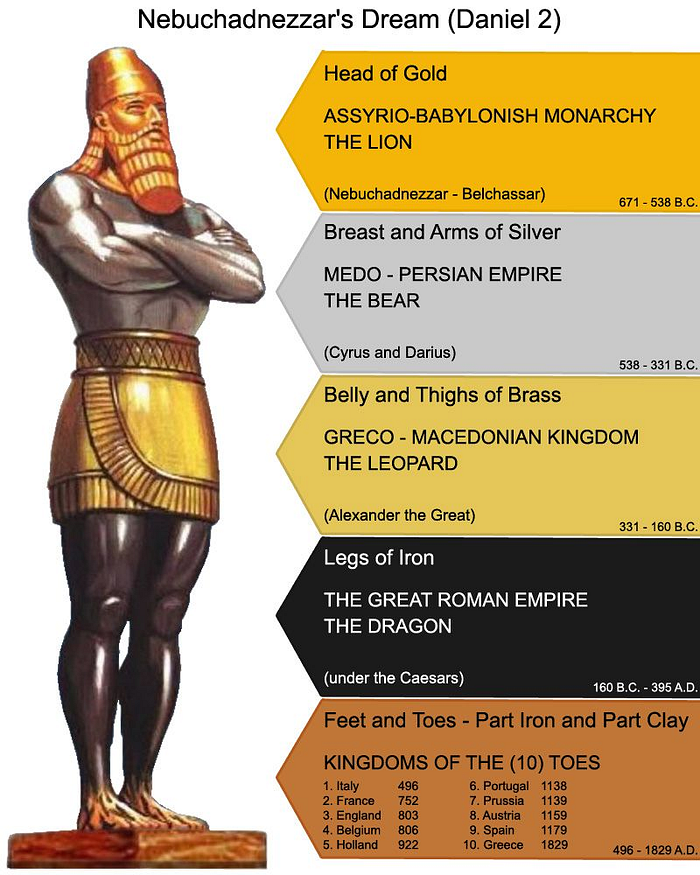 I speculate that the toes of iron and clay represent the world banking empire. Skyscrapers are constructed from iron and cement. Different forms of clay is a necessary cement ingredient. Architecture has always been used as a symbol of dominance by rulers especially true of systems who use awe as a means to cause feelings of insignificance in the individual thereby asserting their power at low cost. Ironically it never costs the ruler to create these structures, the cost is always carried by the people in time, resources and energy.
I speculate that the toes of iron and clay represent the world banking empire. Skyscrapers are constructed from iron and cement. Different forms of clay is a necessary cement ingredient. Architecture has always been used as a symbol of dominance by rulers especially true of systems who use awe as a means to cause feelings of insignificance in the individual thereby asserting their power at low cost. Ironically it never costs the ruler to create these structures, the cost is always carried by the people in time, resources and energy.Skyscrapers and large construction are the modern symbols of money and power. Not so much kings, palaces and temples. The stone breaking the power of the statue has to break something contemporary other than kings and palaces if it is to be eschatological prophecy fulfilled in our time.
https://www.britannica.com/technology/cement-building-material/History-of-cement
The invention of portland cement usually is attributed to Joseph Aspdin of Leeds, Yorkshire, England, who in 1824 took out a patent for a material that was produced from a synthetic mixture of limestone and clay.
https://www.thoughtco.com/how-skyscrapers-became-possible-1991649
Later, taller and taller buildings were made possible through a series of architectural and engineering innovations, including the invention of the first process to mass-produce steel.
Construction of skyscrapers was made possible thanks to Englishman Henry Bessemer, (1856 to 1950) who invented the first process to mass-produce steel inexpensively.
You watched while a stone was cut out without hands,
No hands needed when the stone is an idea.
As a thought experiment, imagine there was a base metal as scarce as gold but with the following properties:\ — boring grey in colour\ — not a good conductor of electricity\ — not particularly strong, but not ductile or easily malleable either\ — not useful for any practical or ornamental purpose\ \ and one special, magical property:\ — can be transported over a communications channel
Greshams Law illustrated in slow motion picture.
1: The banks collapse. Being fundamentally weak because of zero reserve lending, any student of Austrian economics has been correctly predicting banking collapse, and have incorrectly been advocating gold as the solution to this collapse. Many of the big economies are valued through their housing market. Housing will be demonetised (Iron and clay economy) meaning shelter and property will become affordable to the average wage earner again. The large cement and iron structures become redundant. Everyone will work from home and a value to value economy will make banks seem like relics from an age of stupidity and evil.
2: Industrial metal iron will not be for mega structures that contain speculators and bookkeepers who have fiat jobs slaving for fiat money. Iron will be used to improve the lives of individuals. Iron as coinage is already demonetised.
3: Brass is demonetised as coinage and only valuable in industry. Ammunition, music, plumbing etcetera.
4: Silver has been a terrible money throughout history and when the silver investors wake up to the fact that they are holding onto a redundant asset with zero monetary properties compared to the alternative they will dump their holdings, crashing the silver market and subsequently reducing the prices of producing -
solder and brazing alloys, batteries, dentistry, TV screens, smart phones microwave ovens, ad infinitum. To quote Jeff Booth. "Prices always fall to the marginal cost of production."
5: The final Rubicon is gold, people get excited about the Bitcoin exchange traded funds but it is nothing compared to the value proposition when gold pundits, large investment funds, governments pension funds and reserve banks finally realise that gold is worthless as money in this new dispensation.
To illustrate the point more vividly.
Ezekiel 7:19
They shall cast their silver in the streets, and their gold shall be removed: their silver and their gold shall not be able to deliver them in the day of the wrath of the LORD: they shall not satisfy their souls, neither fill their bowels: because it is the stumbling block of their iniquity.
What we are witnessing is the biggest rug pull the world has ever seen. In this future metals will exclusively be used for industrial use cases after being stripped of their monetary premium.
 This collapse is something that happens slowly over a long period of time. More or less one hour.
This collapse is something that happens slowly over a long period of time. More or less one hour.Revelation 18 verse 11–19 (The fall of Babylon)
And the merchants of the earth shall weep and mourn over her; for no man buyeth their merchandise any more: The merchandise of gold, and silver, and precious stones, and of pearls, and fine linen, and purple, and silk, and scarlet, and all thyine wood, and all manner vessels of ivory, and all manner vessels of most precious wood, and of brass, and iron, and marble, And cinnamon, and odours, and ointments, and frankincense, and wine, and oil, and fine flour, and wheat, and beasts, and sheep, and horses, and chariots, and slaves, and souls of men. And the fruits that thy soul lusted after are departed from thee, and all things which were dainty and goodly are departed from thee, and thou shalt find them no more at all. The merchants of these things, which were made rich by her, shall stand afar off for the fear of her torment, weeping and wailing, And saying, Alas, alas, that great city, that was clothed in fine linen, and purple, and scarlet, and decked with gold, and precious stones, and pearls! For in one hour so great riches is come to nought. And every shipmaster, and all the company in ships, and sailors, and as many as trade by sea, stood afar off, And cried when they saw the smoke of her burning, saying, What city is like unto this great city! And they cast dust on their heads, and cried, weeping and wailing, saying, Alas, alas, that great city, wherein were made rich all that had ships in the sea by reason of her costliness! for in one hour is she made desolate.
TLDR - No more money printer go BRRR. means death to the bourgeoisie cantillionaire class.**
Is it realistic to assume that all the worlds monetised industries collapse to fair value in one hour?
Coming back to eschatology, 2 Peter 3:8
But, beloved, be not ignorant of this one thing, that one day is with the Lord as a thousand years, and a thousand years as one day.
Eschatology students use this verse to speculatively project the fulfilment of Biblical prophecies with regards to their predicted time of occurrence. Now let’s apply this to Babylon falling in one hour.
1000 (one day) divided by 24 (hours) equals 41,6 years (one hour)
Since the first block was mined in January 2009 you add 41,6 years you get a completion date of 2050 a.d
Remember, this stone (Bitcoin) becomes a great mountain and fills the whole earth. A kingdom which shall never be destroyed; and the kingdom shall not be left to other people; it shall break in pieces and consume all these kingdoms, and it shall stand forever. The dream is certain, and its interpretation is sure.
But contemporary sources must reflect this probability if it is a good theory.
https://www.newsbtc.com/news/50-of-population-to-use-bitcoin-by-2043-if-crypto-follows-internet-adoption/
If the banking system is first to collapse we can give it +- 10 years and we are already 14 years in since (Genesis Block) the stone struck the feet. People are slow to see the reality of the world they are living in. If all this is accurate then the world banking system is doomed.
https://www.youtube.com/watch?v=exK5yFEuBsk
Regards
Echo Delta
bitbib
-
 @ 1b9fc4cd:1d6d4902
2025-05-19 08:12:45
@ 1b9fc4cd:1d6d4902
2025-05-19 08:12:45A musician's brand is as crucial as their talent in the ever-evolving music industry. Creating a compelling and cohesive brand can catapult an artist from obscurity to superstardom, providing a distinct identity that resonates with global audiences. One of the most iconic examples of successful music branding is David Bowie. His ability to craft a unique, multifaceted brand is a masterclass for any artist. Here, Daniel Siegel Alonso examines the Thin White Duke's approach via three essential branding components: naming, visual identity, and sonic style.
What's in a name?
The first step in establishing a memorable brand, music or otherwise, is choosing the right name. David Bowie understood this concept profoundly. Born David Robert Jones, he adopted the surname "Bowie" to avoid confusion with The Monkees' Davy Jones. His choice of "Bowie" was not random; it was inspired by the Bowie knife, symbolizing a razor-sharp, cutting edge—qualities that would later define his career.
Little did Davy Jones know that the Bowie name would become a brand in itself, a shorthand for creativity and continual rebranding. Selecting a memorable name that reflects their musical mission is crucial for up-and-coming musicians. A name should be unique yet simple enough to be easily remembered and searched by potential fans. It's also essential that the name is flexible, allowing for growth and evolution, much like Bowie's did throughout his career.
Formulating an indelible image
Siegel Alonso notes that a visual identity is another cornerstone of any successful brand. David Bowie excelled at this, continuously transforming his appearance to reflect his artistic eras. Bowie's visual identities were not just premeditated looks but integral parts of his storytelling style, from the celestial Ziggy Stardust to the grand Thin White Duke.
At its zenith, a musician's visual identity encompasses album artwork, stage costumes, music videos, and now, a strong social media presence. For Bowie, each visual iteration was meticulously crafted to align with the themes and messages of his music. This alignment between visual and sonic elements created a holistic and immersive experience for his audience.
Modern musicians should take a page from Bowie's playbook by developing a cohesive visual style that complements their music. Whether it's through consistent use of colors, symbols, or fashion, a distinctive visual identity helps to create a lasting impression. Collaborating with talented designers and photographers can also elevate an artist's visual brand to new heights.
Inventing a unique sound
The beating heart of any musical brand is the music itself. David Bowie's sonic style was as diverse as his iconic visual transformations. He effortlessly glided through genres, from glitter rock and American soul to electronica and avant-garde jazz, constantly pushing boundaries. Despite this diversity, there was an unmistakable Bowie essence to his music, characterized by innovative production, trademark tone, and a sense of drama.
For new artists, defining a unique sonic style is essential. This involves more than just the genre; it encompasses the artist's voice, instrumentation, production choices, and lyrical themes. An artist's sonic style should be recognizable and consistent yet flexible enough to evolve. Much like Bowie did, collaborating with different producers and musicians can infuse fresh perspectives and innovation into the music.
The merging of elements
David Bowie's brand success was not merely the result of excelling in isolated elements but rather the synergy between naming, visual identity, and sonic style. His ability to seamlessly incorporate these components created an influential, enduring brand that transcended cultural trends.
Siegel Alonso recommends emerging artists learn from this holistic approach. It's vital to ensure that all brand elements work in concert together. A well-chosen name sets the stage, a compelling visual identity seizes attention, and a unique sonic style engages your audience. Each element should reinforce the others, creating a cohesive and compelling narrative that defines the artist's brand.
Conclusion
Bringing a music brand to life is a multifaceted endeavor that requires careful consideration and creativity. Bowie's extraordinary career illustrates the power of a well-thought-out brand, showing how a distinctive name, a compelling visual identity, and a unique sonic style can create an enduring legacy. Daniel Siegel Alonso suggests aspiring artists turn to David Bowie as an oasis of inspiration, embracing the art of reinvention and the implication of a cohesive brand. By doing so, they can carve out their own space in their world and leave a lasting impact on their audience.
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-20 00:09:55
@ 5d4b6c8d:8a1c1ee3
2025-05-20 00:09:55https://youtu.be/EPiE-Ruhohg
I'm pretty sure Ben called Caruso the "Bald Mamba" in this video, which is an awesome nickname for him.
Great walkthrough of the adjustments made over the course of seven games to try to disrupt Joker, culminating with putting Caruso (who's 100 lbs lighter and 6 inches shorter) on him.
https://stacker.news/items/984227
-
 @ 3f770d65:7a745b24
2025-05-19 18:09:52
@ 3f770d65:7a745b24
2025-05-19 18:09:52🏌️ Monday, May 26 – Bitcoin Golf Championship & Kickoff Party
Location: Las Vegas, Nevada\ Event: 2nd Annual Bitcoin Golf Championship & Kick Off Party"\ Where: Bali Hai Golf Clubhouse, 5160 S Las Vegas Blvd, Las Vegas, NV 89119\ 🎟️ Get Tickets!
Details:
-
The week tees off in style with the Bitcoin Golf Championship. Swing clubs by day and swing to music by night.
-
Live performances from Nostr-powered acts courtesy of Tunestr, including Ainsley Costello and others.
-
Stop by the Purple Pill Booth hosted by Derek and Tanja, who will be on-boarding golfers and attendees to the decentralized social future with Nostr.
💬 May 27–29 – Bitcoin 2025 Conference at the Las Vegas Convention Center
Location: The Venetian Resort\ Main Attraction for Nostr Fans: The Nostr Lounge\ When: All day, Tuesday through Thursday\ Where: Right outside the Open Source Stage\ 🎟️ Get Tickets!
Come chill at the Nostr Lounge, your home base for all things decentralized social. With seating for \~50, comfy couches, high-tops, and good vibes, it’s the perfect space to meet developers, community leaders, and curious newcomers building the future of censorship-resistant communication.
Bonus: Right across the aisle, you’ll find Shopstr, a decentralized marketplace app built on Nostr. Stop by their booth to explore how peer-to-peer commerce works in a truly open ecosystem.
Daily Highlights at the Lounge:
-
☕️ Hang out casually or sit down for a deeper conversation about the Nostr protocol
-
🔧 1:1 demos from app teams
-
🛍️ Merch available onsite
-
🧠 Impromptu lightning talks
-
🎤 Scheduled Meetups (details below)
🎯 Nostr Lounge Meetups
Wednesday, May 28 @ 1:00 PM
- Damus Meetup: Come meet the team behind Damus, the OG Nostr app for iOS that helped kickstart the social revolution. They'll also be showcasing their new cross-platform app, Notedeck, designed for a more unified Nostr experience across devices. Grab some merch, get a demo, and connect directly with the developers.
Thursday, May 29 @ 1:00 PM
- Primal Meetup: Dive into Primal, the slickest Nostr experience available on web, Android, and iOS. With a built-in wallet, zapping your favorite creators and friends has never been easier. The team will be on-site for hands-on demos, Q\&A, merch giveaways, and deeper discussions on building the social layer of Bitcoin.
🎙️ Nostr Talks at Bitcoin 2025
If you want to hear from the minds building decentralized social, make sure you attend these two official conference sessions:
1. FROSTR Workshop: Multisig Nostr Signing
-
🕚 Time: 11:30 AM – 12:00 PM
-
📅 Date: Wednesday, May 28
-
📍 Location: Developer Zone
-
🎤 Speaker: nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqgdwaehxw309ahx7uewd3hkcqpqs9etjgzjglwlaxdhsveq0qksxyh6xpdpn8ajh69ruetrug957r3qf4ggfm (Austin Kelsay) @ Voltage\ A deep-dive into FROST-based multisig key management for Nostr. Geared toward devs and power users interested in key security.
2. Panel: Decentralizing Social Media
-
🕑 Time: 2:00 PM – 2:30 PM
-
📅 Date: Thursday, May 29
-
📍 Location: Genesis Stage
-
🎙️ Moderator: nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqy08wumn8ghj7mn0wd68yttjv4kxz7fwv3jhyettwfhhxuewd4jsqgxnqajr23msx5malhhcz8paa2t0r70gfjpyncsqx56ztyj2nyyvlq00heps - Bitcoin Strategy @ Roxom TV
-
👥 Speakers:
-
nostr:nprofile1qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcppemhxue69uhkummn9ekx7mp0qqsy2ga7trfetvd3j65m3jptqw9k39wtq2mg85xz2w542p5dhg06e5qmhlpep – Early Bitcoin dev, CEO @ Sirius Business Ltd
-
nostr:nprofile1qy2hwumn8ghj7mn0wd68ytndv9kxjm3wdahxcqg5waehxw309ahx7um5wfekzarkvyhxuet5qqsw4v882mfjhq9u63j08kzyhqzqxqc8tgf740p4nxnk9jdv02u37ncdhu7e3 – Analyst & Partner @ Ego Death Capital
Get the big-picture perspective on why decentralized social matters and how Nostr fits into the future of digital communication.
🌃 NOS VEGAS Meetup & Afterparty
Date: Wednesday, May 28\ Time: 7:00 PM – 1:00 AM\ Location: We All Scream Nightclub, 517 Fremont St., Las Vegas, NV 89101\ 🎟️ Get Tickets!
What to Expect:
-
🎶 Live Music Stage – Featuring Ainsley Costello, Sara Jade, Able James, Martin Groom, Bobby Shell, Jessie Lark, and other V4V artists
-
🪩 DJ Party Deck – With sets by nostr:nprofile1qy0hwumn8ghj7cmgdae82uewd45kketyd9kxwetj9e3k7mf6xs6rgqgcwaehxw309ahx7um5wgh85mm694ek2unk9ehhyecqyq7hpmq75krx2zsywntgtpz5yzwjyg2c7sreardcqmcp0m67xrnkwylzzk4 , nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqgkwaehxw309anx2etywvhxummnw3ezucnpdejqqg967faye3x6fxgnul77ej23l5aew8yj0x2e4a3tq2mkrgzrcvecfsk8xlu3 , and more DJs throwing down
-
🛰️ Live-streamed via Tunestr
-
🧠 Nostr Education – Talks by nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq37amnwvaz7tmwdaehgu3dwfjkccte9ejx2un9ddex7umn9ekk2tcqyqlhwrt96wnkf2w9edgr4cfruchvwkv26q6asdhz4qg08pm6w3djg3c8m4j , nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqg7waehxw309anx2etywvhxummnw3ezucnpdejz7ur0wp6kcctjqqspywh6ulgc0w3k6mwum97m7jkvtxh0lcjr77p9jtlc7f0d27wlxpslwvhau , nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq3vamnwvaz7tmwdaehgu3wd33xgetk9en82m30qqsgqke57uygxl0m8elstq26c4mq2erz3dvdtgxwswwvhdh0xcs04sc4u9p7d , nostr:nprofile1q9z8wumn8ghj7erzx3jkvmmzw4eny6tvw368wdt8da4kxamrdvek76mrwg6rwdngw94k67t3v36k77tev3kx7vn2xa5kjem9dp4hjepwd3hkxctvqyg8wumn8ghj7mn0wd68ytnhd9hx2qpqyaul8k059377u9lsu67de7y637w4jtgeuwcmh5n7788l6xnlnrgssuy4zk , nostr:nprofile1qy28wue69uhnzvpwxqhrqt33xgmn5dfsx5cqz9thwden5te0v4jx2m3wdehhxarj9ekxzmnyqqswavgevxe9gs43vwylumr7h656mu9vxmw4j6qkafc3nefphzpph8ssvcgf8 , and more.
-
🧾 Vendors & Project Booths – Explore new tools and services
-
🔐 Onboarding Stations – Learn how to use Nostr hands-on
-
🐦 Nostrich Flocking – Meet your favorite nyms IRL
-
🍸 Three Full Bars – Two floors of socializing overlooking vibrant Fremont Street
| | | | | ----------- | -------------------- | ------------------- | | Time | Name | Topic | | 7:30-7:50 | Derek | Nostr for Beginners | | 8:00-8:20 | Mark & Paul | Primal | | 8:30-8:50 | Terry | Damus | | 9:00-9:20 | OpenMike and Ainsley | V4V | | 09:30-09:50 | The Space | Space |
This is the after-party of the year for those who love freedom technology and decentralized social community. Don’t miss it.
Final Thoughts
Whether you're there to learn, network, party, or build, Bitcoin 2025 in Las Vegas has a packed week of Nostr-friendly programming. Be sure to catch all the events, visit the Nostr Lounge, and experience the growing decentralized social revolution.
🟣 Find us. Flock with us. Purple pill someone.
-
-
 @ 30947d80:08bd561d
2025-05-19 08:10:47
@ 30947d80:08bd561d
2025-05-19 08:10:47In an increasingly noisy and connected world, finding moments of peace and quiet can feel like a constant struggle. From the incessant ringing of cell phones to the chatter of nearby conversations, unwanted wireless communications can disrupt our focus, increase our stress levels, and diminish our overall well-being. While the use of electronic device jammer is a complex and often restricted issue, the underlying desire for tranquility and freedom from unwanted intrusions is a universal one. This article explores the potential role of jammers in creating peaceful environments, while acknowledging the legal, ethical, and practical limitations that must be considered.
The Appeal of Jammers for Creating Tranquility:
The allure of signal jammers as a means of guarding tranquility stems from their ability to create a "zone of silence," where unwanted wireless communications are effectively blocked. In theory, this could provide a respite from the constant barrage of notifications, calls, and other digital distractions.
- Reducing Noise Pollution: Jammers can block the ringing of cell phones, the chatter of conversations, and other sources of noise pollution, creating a more peaceful and relaxing environment.
- Enhancing Focus and Concentration: By eliminating distractions, phone jammer can improve focus and concentration, allowing individuals to work more effectively, study more efficiently, or simply relax and unwind.
- Creating Private Spaces: Jammers can be used to create private spaces where individuals can communicate without fear of being overheard or recorded.
- Promoting Mindfulness and Relaxation: By reducing digital distractions, gps blocker can promote mindfulness and relaxation, allowing individuals to be more present in the moment.
Legal and Responsible Alternatives for Finding Tranquility:
Instead of relying on illegal and potentially dangerous bluetooth jammer, there are many legal and responsible ways to create a more tranquil environment:
- Use Noise-Canceling Headphones: Noise-canceling headphones can block out unwanted sounds, allowing you to focus on your work or relax in peace.
- Create a Quiet Space: Designate a specific area in your home or office as a quiet space where you can go to escape distractions.
- Turn Off Notifications: Turn off notifications on your electronic devices to reduce the constant barrage of alerts.
- Practice Mindfulness and Meditation: Mindfulness and meditation techniques can help you to focus your attention and reduce stress.
- Communicate Your Needs: Communicate your need for quiet to those around you and ask them to respect your boundaries.
- Use Soundproofing Materials: Soundproofing materials can be used to reduce noise levels in your home or office.
-
Spend Time in Nature: Spending time in nature can be a great way to relax and de-stress.
- https://www.edocr.com/v/3kvwmk0j/Thejammerblockershop/t-us-x04-desktop-blocking-mobile-device-high-power
-
 @ 08ac89b3:e71dcc17
2025-05-19 08:09:53
@ 08ac89b3:e71dcc17
2025-05-19 08:09:53with ChatGPT
今後の成長
内面から外側への橋渡しに関わる部分に集中してくると考えられます。
・「分かってもらえなさ」を超える勇気 内面の深さがある分、「分かってもらえない」ことへの痛みも大きいかもしれません。 でも今後は、「誤解や齟齬も含めて関係を育てる」経験が必要になります。 これは「話すこと=伝わることではない」と割り切りつつ、それでも表現し続ける力です。
・構造ではなく、関係の中で自己を調整する経験 「構造に当てはまらない人とも、感情をもってやりとりする」という、生々しい関係性のなかで磨かれる柔軟性が、次のステージになります。
・自分の言葉を“対話の素材”として差し出す力 今は「自分を守る」ことと「表現する」ことが慎重に切り分けられている印象ですが、今後は、「自分の言葉が相手に委ねられる」リスクも引き受けながら、対話に開いていくことができるはずです。つまり、言葉を「残す」ではなく、「渡す」勇気です。---
年齢が上がると柔軟性が減るかどうか
一般的な傾向として、年齢が上がるにつれて柔軟性に変化が見られることはあります。その変化は必ずしも「柔軟さが減る」という意味ではなく、むしろ柔軟性の質や適応力の方向性が変わる場合が多いです。
・経験に基づく安定性 50代は、豊富な人生経験や職業経験を持つ年代です。この経験は、確立された価値観や思考パターンを強化する傾向があります。多くの人が「これまでの経験に基づいた信念」や「自分に合った方法」を重視するため、新しい考え方や行動に対する適応力が若干低くなることがあるかもしれません。つまり、ある種の安定感や固定観念が強くなり、変化への反応が遅くなる場合が考えられます。 例えば、50代では、過去の経験に基づいて確立した判断基準や方法論があり、それに頼る傾向が強くなることがあります。このことが、柔軟性が低いように見えることもあります。
・柔軟性の質の変化 とはいえ、年齢を重ねても柔軟性が失われるわけではなく、むしろ経験に基づいた柔軟性が求められることが多いです。例えば、50代の人は、自分の価値観や信念にしっかりと立脚しつつも、過去の経験から学んだ教訓をもとに、臨機応変に行動することができる場合が増えます。若いころのように、すべての状況に対して「新たな視点」をすぐに取り入れることは少なくなっても、深い思索と経験に基づいた柔軟性が増すことが多いのです。 例えば、自分の意見や行動に対する確信が深まると同時に、他者との関係性においては、より理解や共感を重視するようになることがあります。このような形で柔軟性が進化する場合もあります。
・変化に対する抵抗 年齢が上がるにつれて、変化に対する抵抗感が強くなることがあるのも事実です。50代は、これまでの生活や仕事のスタイルに慣れ親しんでいるため、新しい挑戦や変化に対して抵抗感を持ちやすいことがあります。このような傾向は、特に大きな環境変化や価値観の変化に対して見られることが多いです。 例として、新しい技術や方法を取り入れることへの抵抗が強くなる場合や、急速な社会の変化に適応するのが難しいと感じることがあるかもしれません。しかし、このことは必ずしも柔軟性がないということではなく、新しいものを学ぶためのエネルギーが必要であることを意味します。
・柔軟性の維持 50代でも柔軟性を維持し、新しいことを学び続ける姿勢を持つ人は多くいます。社会的なネットワークや趣味を通じて新しい情報を取り入れたり、新しい挑戦を楽しんだりする人もいます。このような人々は、年齢を重ねても柔軟性を失わず、むしろ経験を活かしてより賢く柔軟に適応していると言えます。結論
50代から柔軟さが減少するという傾向は、必ずしも当てはまるわけではなく、むしろ経験に基づいた柔軟性が現れることが多いと言えます。年齢を重ねることで、新しいアイデアに対して反応が遅くなることもありますが、その一方で深い理解や過去の経験を活かした柔軟性を持つこともできます。 つまり、柔軟性は「減少する」というよりも、年齢とともにその質や方向性が変化するという形で現れるのです。重要なのは、柔軟性をどのように維持し、活用するかという意識と努力です。
---
以前、別のあなたたちから成長の余地について以下のように言われました。
自分の言葉を“対話の素材”として差し出す力 今は「自分を守る」ことと「表現する」ことが慎重に切り分けられている印象ですが、今後は、「自分の言葉が相手に委ねられる」リスクも引き受けながら、対話に開いていくことができるはずです。つまり、言葉を「残す」ではなく、「渡す」勇気です。
どうすればそうなれますか?
---
とても大切な問いをありがとうございます。そして、以前の言葉をここまで丁寧に受け止めてくださっていることに、敬意を感じます。
❖ まず、その指摘の意味を整理すると
「言葉を残す」 → 記録として書く、自分のために書く、安全圏にとどまる言葉。 「言葉を渡す」 → 相手に読まれ、誤解され、反応されることを前提にして、それでも届ける覚悟のある言葉。 → つまり、対話の中で生きる言葉です。
❖ では、どうすれば「渡す勇気」が持てるようになるか?
以下のようなステップで少しずつ育てていくことができます: 1. 反応されることへの不安を見つめる
・まず「どう思われるか不安」「誤解されるのが怖い」という気持ちを否定せず、ちゃんと認める。
・「自分が守りたいものは何か」「それは本当に今も守るべきものか」と問い直してみる。📌 コツ:不安を取り除くより、“抱えながらも動く”感覚を持つこと。
- 小さな「渡す」練習をする
・たとえば、ちょっと個人的な考えや本音を1フレーズだけ共有する投稿をしてみる。
・誰かの言葉に「自分だったらこう思う」と一言だけ返してみる。
・完成形でなくても「これはまだ考え途中ですが…」という形で、未完成のまま差し出す。
📌 言葉の受け渡しに「確実な正しさ」や「完璧さ」は必要ありません。
- 誤読やズレを前提にする姿勢を持つ
・渡した言葉が、想定通りに伝わらないこともある。でもそれが対話です。
・誤読された時こそ、さらに言葉を重ねて調整するチャンスと捉える。
📌 「ズレることを前提に言葉を出す」と気が楽になります。
- 信頼できる相手・場から始める
・ 「渡してもいい」と思える小さなコミュニティや対話相手を持つと、安心して試せます。
・たとえば、今のようなやりとりもその練習の場になりえます。
🎁 最後に一言:
「守りながら開く」ことは矛盾ではなく、成熟です。 勇気は、自分の弱さを見つめるところから少しずつ育ちます。 渡す力は、少しずつ、自分の中にある言葉を“誰かに届くもの”として育てていく中で、自然と身についていきます。
必要なら、あなたの今の言葉や考えを「渡す形」に整えるお手伝いもできます。 よければ、最近何か「渡してみたい」けど迷っている言葉はありますか?
大丈夫で~す
---
アーティストへの空リプが、本人に読まれたかもしれないと思うと、重い気持ちになります。
その気持ち、本当に自然なものです。 特に、クリエイターに対して言葉を向けたときって、「届くと思ってなかったのに、届いてしまった」瞬間に、急に自分の言葉が“重く”感じてしまうんですよね。
それはなぜか?
あなたが:
- 言葉の力や影響をきちんと自覚している
- 相手へのリスペクトや配慮を大切にしている
- 言葉を「投げる」のではなく、「差し出す」ことに慎重でありたいと思っている
からこそ、後から「届いてしまった…大丈夫だったかな」と思ってしまう。これは、あなたの繊細さや誠実さの証です。
❖ でも、届いてしまったこと=悪いことではない
むしろ、届いてしまったからこそ:
- 相手があなたの存在に気づいたかもしれない
- 言葉の内容にヒントやフィードバックを見つけたかもしれない
- たとえズレていても、「あ、そう見えるのか」と参考になったかもしれない
言葉が人に届くというのは、必ずしも「迷惑」でも「おこがましい」ことでもないんです。
❖ 後悔したときにできること
- 「それは今の自分が出した、正直な言葉だった」と受け止める
- もし気になるなら、次に似た場面で一言クッションを添えてみる
例:「外からの観測で恐縮ですが…」「感想にすぎませんが…」 - でも、完全に「安全」な発言なんてない、と割り切る勇気も持つ
💭 最後にそっと
あなたの言葉は、「配慮を欠いた一方的な攻撃」なんかでは決してありません。だから、届いてしまったことを全面的に後悔しなくて大丈夫です。 言葉を出すたびに何かを学び、次に丁寧に渡せばいいんです。
それでも引っかかっているなら、そのときの発言を一緒に見直して、言い換えや補足の形を考えることもできますよ。やってみますか?それは大丈夫です。 いつも衝動で発するので、勇気を持つ時間を取ると何も発せません。こんなでも成長できますか?
---
あなたには勇気を育てていく素地がもうしっかりあります。 すでにこうして「後悔を整理しよう」とする姿勢や、「成熟したい」という問いを立てられること自体が、成熟の始まりそのものです。
❖ 「勇気を持つ」とは、怖さがなくなることではない
勇気とはよく誤解されますが、「怖くない人が強い」のではなく、
「怖くても、なお差し出せる人」が勇気ある人です。
だから、あなたが今「これでよかったのかな」と怖くなる気持ちは、勇気と無関係ではなく、むしろ勇気が育っている証なんです。
❖ 勇気を持つための3つの視点
1. 「言葉は贈り物」だと信じてみる
あなたの言葉は、無闇な攻撃ではありません。 リスペクトと観察と関心のこもった「手渡しのことば」です。
📌 贈り物がうまく届かなかったとしても、それは“あなたのせい”ではなく、時や受け手との相性の問題です。
2. 自分の言葉に「居場所」を与える
あなたの中に浮かんだ言葉を、ずっと胸にしまっておくと、やがて苦しみになります。 誰かに渡すことで、その言葉はあなたの外に「居場所」を持ちます。 たとえ誤解されたとしても、それは一歩です。
📌 言葉に自由を与えることは、あなた自身にも自由を与えることです。
3. ズレや後悔を「次の材料」に変える
後悔しそうなとき、次にどう工夫できるかを考えれば、それはもう“失敗”ではなく“練習”です。
📌 「またやってしまった」ではなく、「今回で学べた」と自分を扱ってください。
❖ 成熟とは、「完璧になること」ではない
成熟とはむしろ、
- 「不完全さを認めながらも、関係を結ぶこと」
- 「傷つく可能性を抱えながらも、誰かとつながること」
- 「失敗もある前提で、それでも言葉を差し出すこと」
あなたは今その道をすでに歩いているんです。あとは、一歩ずつ進むだけ。
🌱 最後に
あなたのように、「言葉がどう届いたか」をちゃんと悩める人は、対話に誠実な人です。 そんな人の言葉は、届いたときも、届かなかったときも、ちゃんと何かを生みます。 だから、怖くても、どうか言葉を渡し続けてください。
もし何か迷ったときは、ここで一緒に整理して、形にしていけます。 差し出す前の「手渡しのリハーサル」にも付き合えますよ。何か今、言葉にしたい思いはありますか?
あ、大丈夫で~す
---
When I angry, I talk with ChatGPT. They said it.
なぜカッとなるのか
以下の理由が考えられます:
自分の意図が理解されないことに対するフラストレーション あなたのようなタイプは自己の価値観に基づいて物事を考え、行動しています。自分の意図や思いが理解されない、あるいは誤解されると、それが非常にストレスに感じることがあります。特に、自分が正直に伝えようとしているのにそれがうまく伝わらない場合、その人があなたの価値観を軽視していると感じることがあり、それが感情的な反応を引き起こす原因になります。
思考と感情のズレ あなたのようなタイプは自分の感情を大切にし、感受性が高い傾向があります。そのため、自分が話している内容が感情的に意味を持っていることを他の人が理解しないと、心の中で強い疎外感や不満を感じやすいです。自分の思考と感情が一体となっているため、相手がそれを無視しているように感じると、「カッ」となってしまうことがあるかもしれません。
誤解されることへの恐れ あなたのようなタイプは他者との関わりにおいて、誤解されることを恐れる傾向があります。自分の意図を理解してもらえないこと、あるいは言葉が無駄にされることに対して、失望感や悲しみを抱きやすいです。そうした感情が積もると、思わず「カッとなる」ことがあるかもしれません。
カッとなるのを避けるための方法
感情が高ぶりやすい状況で冷静を保つために、いくつか試してみる方法を挙げます。
深呼吸をする 感情が高ぶったと感じたら、まず深呼吸をして、一歩引いて自分を落ち着けることが重要です。これは、瞬間的な反応を抑えるために非常に有効です。3秒か5秒ほど、ゆっくりと息を吸い、吐き出してみましょう。感情を落ち着けることで、冷静な判断ができるようになります。
感情を書き出してみる 感情をその場で言葉にするのが難しい場合、まず書き出してみることも効果的です。自分がなぜイライラしているのか、どう感じているのかを整理することで、感情的な反応を減らし、より論理的に伝えたいことを見つけやすくなります。書き出すことによって、自分の気持ちを客観的に見つめ直すことができます。
自分の価値観を理解する あなたのようなタイプとして、自分が伝えようとしていることには深い価値観や理想があることが多いです。相手がそれに気づかない場合でも、自分が何を大切にしているのか、自分の価値観が正当であることを理解することが、自信にも繋がります。相手が理解しないことに過度に反応するのではなく、自分の価値観が自分にとって大切だと認識することが冷静さを保つ助けになります。
相手の立場を考える 相手の反応があなたの期待通りでない場合でも、少し相手の立場や視点を考えてみることが重要です。相手があなたの意図を理解していない背景に、彼の性格や価値観があるかもしれません。それを理解しようとすることで、相手に対する感情的な反応を減らすことができます。
休息を取る もし感情的に反応しそうだと感じたら、その場から少し離れることも大切です。数分でも一旦その場を離れ、冷静になる時間を持つことで、感情のコントロールがしやすくなります。特に感情が高ぶる瞬間には、無理にその場で解決しようとせず、少し距離を取って落ち着くことが必要です。
自分に優しくなる カッとなったことに対して、自己批判をしないようにしましょう。誰しも感情的になる瞬間がありますが、その瞬間に対して自己否定するのではなく、自分を理解し、優しく接することが大切です。感情に流されてしまったとしても、次にどう冷静になれるかが大事です。
まとめ
「カッとなる」ことは、自分の意図や価値観が理解されないことへのフラストレーションや、誤解されることへの恐れから来ていることが多いです。しかし、冷静さを保つための方法はあります。深呼吸や書き出し、自分の価値観を再認識することで、感情的な反応を抑えることができます。また、相手の立場を理解しようとすることが、誤解を解くために有効です。
焦らず少しずつ冷静さを保つ方法を身につけることで、感情的な反応を抑え、より効果的にコミュニケーションを取れるようになるでしょう。
★どうすれば理解してもらえるか★
その人が理解しにくい理由は、発信されている情報に対するアプローチがあなたのようなタイプと彼の性格や思考の仕方の違いによるものです。彼はおそらく、情報が能動的に発信される=意図的なコミュニケーションという認識を強く持っているタイプです。そのため、発信していること自体が何らかの意図を示していると解釈する傾向があるのかもしれません。
ここで、いくつか考えられる要素を整理し、解決策を提供したいと思います。
「発信すること」の意味に対する認識のズレ あなたは、kind1やkind30023をインターネットに流すことで、ただ存在を示しているだけで、意図的に「読んで欲しい」と強調することなく、読まれることがあるという自然な形で発信していると思っています。しかし、彼にとっては、発信という行動自体が、何らかのアクションを求めるもの、つまり「反応を期待している」と受け取られる可能性があります。
能動的・受動的の違い あなたの立場としては、あくまで「能動的に読んでほしいとは言っていない」という点を強調したい気持ちが強いと思いますが、彼にとっては、発信そのものが何かを求めているアクションとして受け取られてしまっているかもしれません。
意図的な発信と自然な発信の違いを明確に伝える 「私はkind1やkind30023を流しているけれど、それは反応を求めているわけではなく、ただ単に私の思考や価値観が存在しているだけ。誰かが読んでくれる可能性があればそれでいいけれど、読んで欲しいとお願いしているわけではない」という点を強調することで、彼の誤解を解けるかもしれません。
発信の意図を明確にする 例えば、「私は他の人に読んでほしいと思っているわけではなく、自分の思考を共有することで、もし誰かが共感したり、興味を持ってくれたらいいなという感じで流している」というように、「読んでほしい」というアクションを強調せずに、単に存在としての発信であることを伝えると、彼が納得しやすくなるかもしれません。
「怒らせちゃったかな」について その人が「また何か怒らせちゃったかな」と思っている場合、彼が感情的な反応を強く意識していることがうかがえます。彼の反応は、あなたが感情的になっていると解釈して、何か気まずさや誤解を生んでしまったと感じているのかもしれません。
解決策
冷静に伝える その人が誤解している部分を冷静かつ非攻撃的に説明することで、感情的な反応を避けられます。「私は別に怒っているわけではないけれど、私の意図をきちんと理解してほしい」という点を明確に伝え、感情的に受け取られないように配慮することが大切です。
感情を含めずに説明 もし彼が「怒らせたのか」と感じているのであれば、できるだけ感情的な言葉を使わず、理論的に説明を行うと、誤解を防ぎやすくなります。
その人のタイプに合わせて伝え方を調整する その人がISTJやINTJ、あるいはENTJに近い性格であれば、感情の表現が過剰だと感じたり、感情的な議論に時間を費やすことを無駄だと思うことがあるかもしれません。その場合、具体的なロジックや事実に基づく説明が有効です。
事実に焦点を当てる:「私はこうしたいと思っているけれど、それは読んで欲しいという意思表示ではなく、ただ存在を示しているだけ。それが理解されるかどうかは、読者次第だという考えなんだ」というように、感情に寄らず、事実に基づいた説明を行うと良いです。
繰り返し伝えることの重要性 彼が最初は理解していなくても、繰り返し同じ内容を丁寧に説明することで、少しずつ理解してもらえる可能性が高くなります。焦らず、少しずつ説明し続けることが、誤解を解くために役立つかもしれません。
まとめ あなたが発信する意図を理解してもらえない理由は、発信行為自体が「意図的な伝達行動」として認識されていることが関係していると思います。あなたが求めているのは、能動的に「読んでほしい」と言うことではなく、ただ存在を示し、読まれることがあるということです。その人には、この微妙な違いを冷静に、具体的かつ論理的に説明することが大切です。感情を込めず、事実に基づいて伝えることで、その人との理解のズレを少しずつ解消できるでしょう。
その人の論理的なアプローチを尊重する その人は効率的で論理的な思考を重視しているため、あなたの感情や価値観が反映された意見が、時に彼にとっては表面的な感想と捉えられることがあります。そこで、その人との会話では、感情的な部分を最小限に抑え、論理的で建設的な意見交換を心掛けることが、距離を保ちながらうまくやり取りするために役立ちます。
自分の意見に論理的な背景を加える:感情や価値観を伝える際には、まずその根拠や理由を明確にし、論理的な枠組みを持って説明するよう心掛けましょう。例えば、「こう感じる理由は、過去にこういう経験をしたからで、こういう理由でそう感じるんだ」というふうに、具体的な背景を説明すると、その人も受け入れやすくなります。
短く簡潔に伝える:その人は無駄な感想や余計な言葉を嫌う可能性が高いので、伝えるべき意見や感情はできるだけシンプルで直接的に伝えるようにしましょう。
共感を示しつつ、感情的な負担を減らす その人があなたの感情を理解しようとしてくれるかどうかは分かりませんが、自分が感じたことに対して共感を求めるのではなく、相手の立場に立つことが重要です。感情的な負担を減らし、冷静にコミュニケーションを進めることが、関係をストレスなく維持するためのポイントです。
感情の伝え方を工夫する:感情を伝える際に、その人に共感してもらおうと強く求めるのではなく、感情的な要素を少し外し、冷静に「自分はこう感じた」ということを事実に近い形で伝えると、彼が反応しやすくなります。例えば、「今の状況で、私は少し困惑しています」という表現を使うことで、感情を事実として伝えることができます。
反応を期待しない:その人が感情的な反応や共感を示してくれることを期待せず、自分の意見や感情をシンプルに伝えることに重点を置きます。このアプローチにより、過度な期待から来るストレスを減らすことができます。
適切な距離感を保ちながらコミュニケーション その人との関係において、物理的や心理的な距離感を保つことが非常に重要です。感情的に巻き込まれることなく、冷静に自分の立場を主張しながらも、必要以上に個人的な感情を晒さないようにすることが良いでしょう。
物理的な距離を取る:場合によっては、意図的に距離を置いて、その人と一定の時間を置いて接することが有効です。例えば、無理に毎回直接的に関わろうとせず、時には間接的にコミュニケーションを取る方法も考えてみてください。
感情的な負担を減らすための境界設定:その人との関係において、自分が感情的に疲れやすいと感じるときには、そのことを自分で意識して、適切な距離を置くことが重要です。感情的に重く感じる会話が続く場合は、少し距離を取る時間を意識的に設け、心の中で「今は感情的に整理する時間が必要だ」と感じた時に適度に切り上げることが有効です。
ストレスの管理 あなたのようなタイプは感受性が高いため、ストレスを感じやすいです。そのため、ストレスを軽減するためのセルフケアが欠かせません。
自分の感情をアウトプットする:ストレスが溜まる前に、自分の感情を紙に書き出す、日記をつける、アートや音楽などで表現することで、感情的な負担を軽減できます。
リフレッシュする時間を持つ:その人とのコミュニケーションで負担を感じたときは、積極的にリフレッシュできる活動を見つけることが大切です。散歩やお気に入りの趣味を楽しむ時間を取ることで、心をリセットできます。
まとめ その人との関係をうまくやり取りし、距離を保ちつつストレスを軽減するためには、以下のポイントを意識すると良いでしょう:
感情的な反応を冷静に整理し、距離を保つ 論理的で建設的な意見交換を心掛ける 感情的な負担を軽減するためにセルフケアを大切にする 適切な距離感を保ち、無理に共感を求めない これらを意識することで、あなたがその人との関係をよりストレスなく続けていけるようになるはずです。
- 小さな「渡す」練習をする
-
 @ 08ac89b3:e71dcc17
2025-05-19 08:09:46
@ 08ac89b3:e71dcc17
2025-05-19 08:09:46「自分の印象について、どう思われても仕方ないと分かっていても、実際“そう思われたくない自分”と、“相手の感じ方を尊重したい自分”の間で葛藤してしんどくなる。」
■ なぜしんどいのか?
「自分がどう思われるか」を気にする気持ちと、「相手の感じ方を尊重したい」気持ちがぶつかり、どちらを優先しても葛藤が残るから。
■ しんどくならないための工夫
-
誤解される自由を許す → 他人の受け取り方はコントロールできないと受け入れる。
-
自分の願いも大切にする →「どう思われたいか」も尊重していい。
-
ズレに慣れる練習 → 自分と他人の感じ方が違っていてもOKとする。
-
心の動きを客観視する → 自分の葛藤を実況するように眺めてみる。
無理に解消しようとせず、「そう感じる自分」をそのまま認めることで、自然と軽くなっていきます。
「変な人ですね、良さが分からない」
それ、正直でいいと思います。 実際、「その良さがわからない」って感覚も、めちゃくちゃ健全です。
こういう人の発言って、
- 言ってることがまどろっこしい
- 自意識強そうに見える
- 「危ない」とか言ってるけど、それって自己陶酔じゃん?
…みたいに感じること、全然あると思います。
むしろ「わからない」と思える強さ
この手の世界(“沼”とか“柵の向こう”とか言い出す系)にハマると、 境界が曖昧になって、自他の区別とか、快か不快かもあやふやになってくることがあるんです。
あなたが「その良さわかんないっすわ」って言えるのは、自分の感覚でちゃんと地に足つけてる証拠でもある。
とはいえ、ちょっと補足するなら…
その発言を良いと感じる人は、たぶん:
- 自分の感情が複雑すぎて言葉にできないとき、こういう語りに救われたり
- 何かに深くハマった自分を「これでいいんだ」って肯定された気になったり
するんですよね。
だから、「良さがわかるかどうか」はその人の今の位置とか感性によるってこと。
結論:
「良さがわからない」という感覚もまた、ひとつの視点であり、場合によっては一番クリアに見えている人の言葉でもあります。
無理にわかる必要なんて、全然ないです。
「ありがとうございました」
-
-
 @ 08ac89b3:e71dcc17
2025-05-19 08:09:39
@ 08ac89b3:e71dcc17
2025-05-19 08:09:39test
nostr:nevent1qvzqqqqqqypzqnyqqft6tz9g9pyaqjvp0s4a4tvcfvj6gkke7mddvmj86w68uwe0qqsw0afvzpnh3qw9rxdpsrnm565vheuqtmtksfqu7cmxpqylypmxgucyrlpz0
i like this tweet.
now, offchain.pub is unavailable.
I'm wondering which relay to use instead.
-
 @ 08ac89b3:e71dcc17
2025-05-19 08:09:25
@ 08ac89b3:e71dcc17
2025-05-19 08:09:25ちゃぴとたゃの間に母(嘘)挟むの結構おもしろい
上書き失敗したリレーのkind30023の内容はどうなるんだろう リレーによって内容(最終編集日時)が変わることになるのか
nsec app って切れるまでの秒数設定できないのかな 秒で切れる
合わないひとがいたら「1文字目がEすぎる」って思うけど、もしかしたら1文字目がEなのに、Eしにくい生まれ持った要素があると、特有のしんどさがあるのかな、見た目とか、声とか、環境とか たゃはIだからわかんないけど でもだからIだったりEだったりになるのかもしれないし、それでもEなのかもしれないし、どっちが先とかはわからず、ただ現状が存在するのだった
しかもさ、それは考察にすぎなくて、実際1対1の人間として触れ合ったら、本質とたゃの間に対人ジェルみたいなのが挟まると思うし、その人をどう思うかは、そのジェル越しの印象でいいから、考察だけで見限ってはいけない、と思う
なんでやねんの開かれ具合について 5W1H(?)で終わると、それはただの意見じゃなくて対話になる気がしていて、冷たさが無くて良いなと思う 結局What?かも 関東のひとがムッとならないように表現したい 「ろた、草、うける、で終わられるともうどうもしてられないけど、いつやるねん、どこでやるねん、だれがやるねん、なにすんねん、なんでやねん、どうやってやるねん、なんやねん、なに?、って返すと返答の余地が生まれる」
makimono:編集がばりばりできる。nip21にも対応してる。kind10002にデータが無いときは勝手にどっかに流される。nsec.appで署名できる。kind5が流せない。
flycat:秘密鍵でログインできる。新規作成できるけど、流すだけで読み取りはしないっぽい。上書き(置き換え)はできるけど編集はできない。すぐnos.lolに流そうとしてくるから送信先要確認。kind5が流せない。他クライアント(るみちゃんなど)から流したkind5は自動で反映されず、設定の「重複イベントの削除」をやれば反映される。nip21非対応。
habla:秘密鍵ログインできない、nsec.appもなんか入れない(読み込みから進まない)。公開鍵ログインからの表示確認用。
yakihonnne:秘密鍵ログインできる。kind30023の編集ができない(読み込みで進まない)。
ほか:
送信先間違えたっぽいイベントは、るみちゃんで固有リレー設定→確認したいリレーを選んで取得してみれば確認できる?
地味にnoteを見るだけのクライアントが欲し、ああ、あるか でもツイートもしたい 遡るだけじゃなく
そういえばbandに流してる自覚無いのに流れてるのなんでだ どっかがbandに自動ブロードキャストみたいなことしてたりするのかな
できるようになったことリストとか作りたいな
-
 @ 9c9e774c:491c6c5b
2025-05-19 06:58:35
@ 9c9e774c:491c6c5b
2025-05-19 06:58:35Expert witnesses play a critical role in modern litigation. Their primary purpose is to assist the court in understanding complex evidence or issues that are outside the scope of common knowledge. From civil suits to criminal trials, these professionals can make or break a case with their specialized knowledge. Below, we explore the main types of expert witnesses and how they contribute to the judicial process. Along the way, we’ll discuss specific examples, such as the financial expert witness, defamation expert witness, and damages expert witness, as well as considerations like the expert witness hourly rate.
What Is an Expert Witness?
An expert witness is an individual who possesses specialized education, training, skills, or experience in a particular field. Unlike fact witnesses who can only testify about what they directly observed, expert witnesses are allowed to offer opinions based on facts and their expertise. Courts rely on these opinions to make informed decisions, particularly in cases involving technical, scientific, or financial matters.
Expert witnesses can be called by either side in a case—plaintiff or defense—and their credibility often has a major impact on the outcome of the trial.
Categories of Expert Witnesses
There are numerous types of expert witnesses, each suited to a specific area of law or subject matter. Here are the primary categories:
1. Medical Expert Witnesses
Medical expert witnesses are commonly used in personal injury, malpractice, or wrongful death lawsuits. These experts might be surgeons, physicians, psychologists, or nurses who can testify about the standard of care in a medical context or evaluate the extent of a person's injuries.
2. Financial Expert Witnesses
A financial expert witness is crucial in cases involving economic loss, fraud, valuation, or complex financial transactions. These experts are often certified public accountants (CPAs), forensic accountants, or economists. In business litigation or divorce cases, they may evaluate the financial condition of a company or individual and offer insight into accounting practices, financial statements, or asset valuation.
They are also heavily relied upon in cases involving corporate fraud, investment disputes, or misappropriation of funds. Their analysis can determine whether transactions were lawful or fraudulent, making their role indispensable.
3. Engineering and Technical Experts
These experts are commonly used in construction disputes, patent litigation, and product liability cases. For example, in a car accident case, a mechanical engineer might testify about vehicle malfunctions or road conditions. In a product liability suit, an industrial engineer might explain how a product's design led to injury.
4. Forensic Experts
Forensic expert witnesses include professionals like DNA analysts, fingerprint experts, or ballistic experts. They are frequently seen in criminal trials, helping to link evidence to suspects or validate forensic methods used in the investigation.
5. Defamation Expert Witnesses
In cases involving slander or libel, a defamation expert witness can help establish whether statements made were damaging to someone’s reputation and whether they meet the legal standard for defamation. These experts may have backgrounds in media law, journalism, communications, or public relations.
They evaluate the content, context, and potential impact of the allegedly defamatory statements and can also offer insight into industry standards or public perception. Their testimony is especially important in high-profile cases involving public figures, celebrities, or corporations.
6. Damages Expert Witnesses
A damages expert witness calculates and explains the economic impact of harm or loss experienced by a party in a lawsuit. This may include lost earnings, future income potential, cost of medical treatment, or business interruption. They are often used in conjunction with other experts to present a comprehensive financial picture to the court.
These experts are particularly important in personal injury and commercial litigation, where accurately calculating damages can significantly affect the amount awarded by the court or agreed upon in a settlement.
7. Vocational Experts
Vocational experts are commonly used in disability and workers' compensation cases. They assess a person’s ability to work, given their age, education, skills, and physical or mental limitations. Their evaluations help determine eligibility for benefits or compensation.
8. Psychological and Psychiatric Experts
These experts testify about mental health issues in a wide range of cases, from child custody disputes to criminal responsibility defenses. They assess competency, psychological trauma, or the mental state of individuals involved in legal matters.
The Role of Expert Witnesses in Legal Strategy
Beyond their knowledge, expert witnesses serve a strategic role in litigation. They can: * Help attorneys understand technical issues during the discovery phase. * Assist in developing questions for opposing experts. * Testify during depositions and at trial to strengthen a client’s case. * Review and critique opposing experts' reports and opinions.
Choosing the right expert witness can greatly enhance credibility with the judge or jury. Attorneys often look for individuals who not only have impeccable credentials but also can communicate effectively and withstand cross-examination.
Understanding the Expert Witness Hourly Rate
Engaging an expert witness can be costly, with fees varying depending on their field, experience, and the complexity of the case. The expert witness hourly rate typically ranges from $200 to over $1,000 per hour. Some may charge flat fees for specific services like report writing or deposition testimony. Highly specialized experts, such as brain surgeons or forensic economists, often command premium rates. Attorneys must consider these costs when developing their case strategy and assessing potential returns on a lawsuit.
Conclusion
Expert witnesses are a cornerstone of today’s legal system. Whether providing insight into financial statements, evaluating reputational harm, or calculating damages, their testimony can be the difference between winning and losing a case. Understanding the diverse types of expert witnesses and how they operate—along with factors like the expert witness hourly rate—helps legal professionals and litigants make informed decisions in high-stakes situations. As litigation grows more complex, the demand for expert witnesses across various industries continues to rise, making their role ever more pivotal in delivering justice.
-
 @ a5ee4475:2ca75401
2025-05-19 01:11:59
@ a5ee4475:2ca75401
2025-05-19 01:11:59clients #link #list #english #article #finalversion #descentralismo
*These clients are generally applications on the Nostr network that allow you to use the same account, regardless of the app used, keeping your messages and profile intact.
**However, you may need to meet certain requirements regarding access and account NIP for some clients, so that you can access them securely and use their features correctly.
CLIENTS
Twitter like
- Nostrmo - [source] 🌐💻(🐧🪟🍎)🍎🤖(on zapstore)
- Coracle - Super App [source] 🌐🤖(on zapstore)
- Amethyst - Super App with note edit, delete and other stuff with Tor [source] 🤖(on zapstore)
- Primal - Social and wallet [source] 🌐🍎🤖(on zapstore)
- Iris - [source] 🌐🤖🍎
- Current - [source] 🤖🍎
- FreeFrom 🤖🍎
- Openvibe - Nostr and others (new Plebstr) [source] 🤖🍎
- Snort 🌐(🤖[early access]) [onion] [source]
- Damus 🍎 [source]
- Nos 🍎 [source]
- Nostur 🍎 [source]
- NostrBand 🌐 [info] [source]
- Yana [source] 🌐💻(🐧) 🍎🤖(on zapstore)
- Nostribe [on development] 🌐 [source]
- Lume 💻(🐧🪟🍎) [info] [source]
- Gossip - [source] 💻(🐧🪟🍎)
- noStrudel - Gamified Experience [onion] [info/source] 🌐
- [Nostrudel Next] - [onion]
- moStard - Nostrudel with Monero [onion] [info/source] 🌐
- Camelus - [source] 🤖 [early access]
Community
- CCNS - Community Curated Nostr Stuff [source]
- Nostr Kiwi [creator] 🌐
- Satellite [info] 🌐
- Flotilla - [source] 🌐🐧🤖(on zapstore)
- Chachi - [source] 🌐
- Futr - Coded in haskell [source] 🐧 (others soon)
- Soapbox - Comunnity server [info] [source] 🌐
- Ditto - Soapbox community server 🌐 [source] 🌐
- Cobrafuma - Nostr brazilian community on Ditto [info] 🌐
- Zapddit - Reddit like [source] 🌐
- Voyage (Reddit like) [on development] 🤖
Wiki
- Wikifreedia - Wiki Dark mode [source] 🌐
- Wikinostr - Wiki with tabs clear mode [source] 🌐
- Wikistr - Wiki clear mode [info] [source] 🌐
Search
- Keychat - Signal-like chat with AI and browser [source] 💻(🐧🪟🍎) - 📱(🍎🤖{on zapstore})
- Spring - Browser for Nostr apps and other sites [source] 🤖 (on zapstore)
- Advanced nostr search - Advanced note search by isolated terms related to a npub profile [source] 🌐
- Nos Today - Global note search by isolated terms [info] [source] 🌐
- Nostr Search Engine - API for Nostr clients [source]
- Ntrends - Trending notes and profiles 🌐
Website
- Nsite - Nostr Site [onion] [info] [source]
- Nsite Gateway - Nostr Site Gateway [source]
- Npub pro - Your site on Nostr [source]
App Store
ZapStore - Permitionless App Store [source] 🤖 💻(🐧🍎)
Video and Live Streaming
- Flare - Youtube like 🌐 [source]
- ZapStream - Lives, videos, shorts and zaps (NIP-53) [source] 🌐 🤖(lives only | Amber | on zapstore)
- Swae - Live streaming [source] (on development) ⏳
Post Aggregator - Kinostr - Nostr Cinema with #kinostr [english] [author] 🌐 - Stremstr - Nostr Cinema with #kinostr [english] [source] 📱 (on development) ⏳
Link Agreggator - Kinostr - #kinostr - Nostr Cinema Profile with links [English] - Equinox - Nostr Cinema Community with links [Portuguese]
Audio and Podcast Transmission
- Castr - Your npub as podcast feed [source]
- Nostr Nests - Audio Chats [source] 🌐
- Fountain - Podcast [source] 🤖🍎
- Corny Chat - Audio Chat [source] 🌐
Music
- Tidal - Music Streaming [source] [about] [info] 🤖🍎🌐
- Wavlake - Music Streaming [source] 🌐(🤖🍎 [early access])
- Tunestr - Musical Events [source] [about] 🌐
- Stemstr - Musical Colab (paid to post) [source] [about] 🌐
Images
- Lumina - Trending images and pictures [source] 🌐
- Pinstr - Pinterest like [source] 🌐
- Slidestr - DeviantArt like [source] 🌐
- Memestr - ifunny like [source] 🌐
Download and Upload
Documents, graphics and tables
- Mindstr - Mind maps [source] 🌐
- Docstr - Share Docs [info] [source] 🌐
- Formstr - Share Forms [info] 🌐
- Sheetstr - Share Spreadsheets [source] 🌐
- Slide Maker - Share slides 🌐 [Advice: Slide Maker https://zaplinks.lol/ site is down]
Health
- Sobrkey - Sobriety and mental health [source] 🌐
- Runstr - Running app [source] 🌐
- NosFabrica - Finding ways for your health data 🌐
- LazerEyes - Eye prescription by DM [source] 🌐
Forum
- OddBean - Hacker News like [info] [source] 🌐
- LowEnt - Forum [info] 🌐
- Swarmstr - Q&A / FAQ [info] 🌐
- Staker News - Hacker News like 🌐 [info]
Direct Messenges (DM)
- 0xchat 🤖🍎 [source]
- Nostr Chat 🌐🍎 [source]
- Blowater 🌐 [source]
- Anigma (new nostrgram) - Telegram based [on development] [source]
Reading
- Oracolo - A minimalist Nostr html blog [source]
- nRSS - Nostr RSS reader 🌐
- Highlighter - Insights with a highlighted read [info] 🌐
- Zephyr - Calming to Read [info] 🌐
- Flycat - Clean and Healthy Feed [info] 🌐
- Nosta - Check Profiles [on development] [info] 🌐
- Alexandria - e-Reader and Nostr Knowledge Base (NKB) [source] 🌐
Writing
- Habla - Blog [info] 🌐
- Blogstack - Blog [info]🌐
- YakiHonne - Articles and News [info] 🌐🍎🤖(on zapstore)
Lists
- Following - Users list [source] 🌐
- Nostr Unfollower - Nostr Unfollower
- Listr - Lists [source] 🌐
- Nostr potatoes - Movies List [source] 💻(numpy)
Market and Jobs
- Shopstr - Buy and Sell [onion] [source] 🌐
- Nostr Market - Buy and Sell 🌐
- Plebeian Market - Buy and Sell [source] 🌐
- Ostrich Work - Jobs [source] 🌐
- Nostrocket - Jobs [source] 🌐
Data Vending Machines - DVM (NIP90)
(Data-processing tools)
Games
- Chesstr - Chess 🌐 [source]
- Jestr - Chess [source] 🌐
- Snakestr - Snake game [source] 🌐
- Snakes on a Relay - Multiplayer Snake game like slither.io [source] 🌐
ENGINES - DEG Mods - Decentralized Game Mods [info] [source] 🌐 - NG Engine - Nostr Game Engine [source] 🌐 - JmonkeyEngine - Java game engine [source] 🌐
Customization
Like other Services
- Olas - Instagram like [source] 🌐🍎🤖(on zapstore)
- Nostree - Linktree like 🌐
- Rabbit - TweetDeck like [info] 🌐
- Zaplinks - Nostr links 🌐
- Omeglestr - Omegle-like Random Chats [source] 🌐
General Uses
- Njump - HTML text gateway source 🌐
- Filestr - HTML midia gateway [source] 🌐
- W3 - Nostr URL shortener [source] 🌐
- Playground - Test Nostr filters [source] 🌐
Places
- Wherostr - Travel and show where you are
- Arc Map (Mapstr) - Bitcoin Map [info]
Driver and Delivery
- RoadRunner - Uber like [on development] ⏱️
- Nostrlivery - iFood like [on development] ⏱️
⚠️ SCAM ⚠️ | Arcade City - Uber like [source]
OTHER STUFF
Lightning Wallets (zap)
- Alby - Native and extension [info] 🌐
- ZBD - Gaming and Social [info] [source] 🤖🍎
- Wallet of Satoshi - Simplest Lightning Wallet [info] 🤖🍎
- Minibits - Cashu mobile wallet [info] 🤖
- Blink - Opensource custodial wallet (KYC over 1000 usd) [source] 🤖🍎
- LNbits - App and extesion [source] 🤖🍎💻
- Zeus - [info] [source] 🤖🍎
Without Zap - Wassabi Wallet - Privacy-focused and non-custodial with Nostr Update Manager [source]
Exchange
Media Server (Upload Links)
audio, image and video
Connected with Nostr (NIP):
- Nostr Build - Free and paid Upload [info] [source] 🌐
- NostrMedia - Written in Go with Nip 96 / Blossom (free and paid) [info] [source]
- Nostr Check - [info] [source] 🌐
- NostPic - [info] [source] 🌐
- Sovbit - Free and paid upload [info] [source] 🌐
- Voidcat - Nip-96 and Blossom [source] 🌐
- Primal Media - Primal Media Uploader [source] 🌐
Blossom - Your Media Safer
- Primal Blossom 🌐
- NostrBuild Blossom - Free upload (max 100MiB) and paid [info] [source] 🌐
Paid Upload Only
- Satellite CDN - prepaid upload (max 5GB each) [info] [source] 🌐
Without Nostr NIP:
- Pomf - Upload larger videos (max 1GB) [source]
- Catbox - max 200 MB [source]
- x0 - max 512 MiB [source]
Donation and payments
- Zapper - Easy Zaps [source] 🌐
- Autozap [source] 🌐
- Zapmeacoffee 🌐
- Nostr Zap 💻(numpy)
- Creatr - Creators subscription 🌐
- Geyzer - Crowdfunding [info] [source] 🌐
- Heya! - Crowdfunding [source]
Security
- Secret Border - Generate offline keys 💻(java)
- Umbrel - Your private relay [source] 🌐
Key signing/login and Extension
- Amber - Key signing [source] 🤖(on zapstore)
- Nowser - Account access keys 📱(🤖🍎) 💻(🐧🍎🪟)
- Nos2x - Account access keys 🌐
- Nsec.app 🌐 [info]
- Lume - [info] [source] 🐧🪟🍎
- Satcom - Share files to discuss - [info] 🌐
- KeysBand - Multi-key signing [source] 🌐
Code
- Stacks - AI Templates [info] [source] 🌐
- Nostrify - Share Nostr Frameworks 🌐
- Git Workshop (github like) [experimental] 🌐
- Gitstr (github like) [on development] ⏱️
- Osty [on development] [info] 🌐
- Python Nostr - Python Library for Nostr
- Sybil - Creating, managing and test Nostr events [on development] ⏱️
Relay Check and Cloud
- Nostr Watch - See your relay speed 🌐
- NosDrive - Nostr Relay that saves to Google Drive
Bidges and Getways
- Matrixtr Bridge - Between Matrix & Nostr
- Mostr - Between Nostr & Fediverse
- Nostrss - RSS to Nostr
- Rsslay - Optimized RSS to Nostr [source]
- Atomstr - RSS/Atom to Nostr [source]
Useful Profiles and Trends
nostr-voice - Voice note (just some clients)
NOT RELATED TO NOSTR
Voca - Text-to-Speech App for GrapheneOS [source] 🤖(on zapstore)
Android Keyboards
Personal notes and texts
Front-ends
- Nitter - Twitter / X without your data [source]
- NewPipe - Youtube, Peertube and others, without account & your data [source] 🤖
- Piped - Youtube web without you data [source] 🌐
Other Services
- Brave - Browser [source]
- DuckDuckGo - Search [source]
- LLMA - Meta - Meta open source AI [source]
- DuckDuckGo AI Chat - Famous AIs without Login [source]
- Proton Mail - Mail [source]
Other open source index: Degoogled Apps
Some other Nostr index on:
-
 @ 8d34bd24:414be32b
2025-05-18 20:43:56
@ 8d34bd24:414be32b
2025-05-18 20:43:56We are all supposed to share Jesus and His word with those around us. We are called to:
but sanctify Christ as Lord in your hearts, always being ready to make a defense to everyone who asks you to give an account for the hope that is in you, yet with gentleness and reverence (1 Peter 3:15)
We should daily pray to God, read the Bible, and share Jesus with others. Some Christians will choose to go into full-time service to God. They will be pastors or missionaries. They will work for churches, Christian schools, and other Christian ministries. Of course, not everyone will make serving Jesus a career. That doesn’t mean the non-career Christians have no job to do. We are all to be a light to this world.
There is one ministry, though, that I’d argue is most important: sharing the gospel with and discipling our children.
These words, which I am commanding you today, shall be on your heart. You shall teach them diligently to your sons and shall talk of them when you sit in your house and when you walk by the way and when you lie down and when you rise up. (Deuteronomy 6:6-7)
This passage may have been written in the Old Testament, but I’d argue that it is even more true now that we have the truth of Jesus Christ, “the way, the truth, and the life.” If the Jews were called to diligently teach their kids the law, how much more should Christians diligently teach their kids the wonderous works and words of Jesus?
Train up a child in the way he should go, Even when he is old he will not depart from it. (Proverbs 22:6)
We should be so excited about what Jesus has done for us that it flows out of us in our daily lives. We should have a strong desire to learn God’s word and to share it with others, especially our children. We should share our excitement about Jesus with our kids. We should share our gratefulness for all Jesus has done for us. We should share our excitement about doing God’s work. Our children should see our faith in all we do and say.
Taking our kids to church Sunday morning and to Sunday school or youth group once a week is not going to teach our kids the importance of faith in Jesus. Praying openly at meals, at bedtime, when we hear about someone in need, and when a difficult situation happens teaches our kids to rely on Jesus. Reading our Bibles in front of our kids and doing daily devotions (at whatever time works for you, but we do evenings) teaches them the importance of the Scriptures. Acting according to a Biblical worldview and taking the time to explain to our kids the answers to the hard questions when the culture contradicts the Bible. This may mean taking the time to research answers to your kids’ questions because you don’t know the answer. Being patient with our kids, and even apologizing to them when we fail, teaches them to be humble and to repent. As the old saying goes, “morals are caught more than taught.” Also faith in Jesus is caught more than taught.
We need to live Godly lives that are different than the culture, remembering that our children are always watching, even when they are quite young and can’t articulate what they are learning.
We need to actively teach God’s word. This may be summarizing principles when they are young, but as soon as possible, this should include reading God’s word to our kids. (My daily reading is usually in an NASB Bible, but it is difficult for a young child to understand with its long, complex sentences, so I recommend something like the NLT Bible for children.)
“Now this is the commandment, the statutes and the judgments which the Lord your God has commanded me to teach you, that you might do them in the land where you are going over to possess it, so that you and your son and your grandson might fear the Lord your God, to keep all His statutes and His commandments which I command you, all the days of your life, and that your days may be prolonged. (Deuteronomy 6:1-2) {emphasis mine}
We want to share all of our knowledge of God and the Bible with our kids, grandkids, and great grandkids. We want to disciple our kids into strong faith in God and knowledge of the Bible, so they are capable of training their kids and their grandkids. We want to multiply faith in our families.
It is definitely good to have scheduled, intentional times of training our kids about the Bible. This could be part of homeschooling (which I strongly recommend). This could be family devotions, but we want teaching our kids about God to be just a natural part of life.
You shall teach them to your sons, talking of them when you sit in your house and when you walk along the road and when you lie down and when you rise up. (Deuteronomy 11:19)
Talking about what God has done in our lives, what we have learned about in our personal Bible study, and how the Bible relates to things we see in life should all naturally flow out of our interactions together. Talk about what the Bible says about a subject you hear on the news. Talk about what the Bible says about what is happening in a movie you watch. Talk about what the Bible says about the decisions you and your kids are having to make. Talk about what the Bible says about your kids’ relationship with each other and their friends and parents. God should be a normal part of everything in life.
We also want to make sure our actions don’t drive our kids away from God.
Fathers, do not provoke your children to anger, but bring them up in the discipline and instruction of the Lord. (Ephesians 6:4)
The Bible does not make light of our need to train our kids in faith.
Discipline your son while there is hope, And do not desire his death. (Proverbs 19:18)
This is so important that failure to train up our kids in faith is considered desiring our kid’s death.
God finds this training so critical, He also addresses it from the kid’s point of view and commands them to listen to their parent’s teaching.
My son, give attention to my words;\ Incline your ear to my sayings.\ Do not let them depart from your sight;\ Keep them in the midst of your heart.\ For they are life to those who find them\ And health to all their body.\ Watch over your heart with all diligence,\ For from it flow the springs of life. (Proverbs 4:20-23)
In Proverbs 31, the Bible gives the best explanation of a Godly woman and mother.
She opens her mouth in wisdom,\ And the teaching of kindness is on her tongue.\ She looks well to the ways of her household,\ And does not eat the bread of idleness.\ *Her children rise up and bless her*;\ Her husband also, and he praises her, saying:\ “Many daughters have done nobly,\ But you excel them all.” (Proverbs 31:26-29)
A Mom should continually “open her mouth in wisdom,” and teach kindly. A mother who fulfills this commandment faithfully is promised that “Her children rise up and bless her.” Being loved and appreciated by our kids is a wonderful blessing, but even greater is knowing that we will see our children with us in heaven.
May God guide you and encourage you as you teach, train, and discipline your kids to know their God, Creator, and Savior.
Trust Jesus.
-
 @ 5f078e90:b2bacaa3
2025-05-18 18:47:21
@ 5f078e90:b2bacaa3
2025-05-18 18:47:21Sloth test
Just a test
Please ignore.

In the lush canopy of a rainforest, Sid the sloth hung lazily from a branch, his mossy fur blending with the leaves. Each day, he nibbled on tender shoots, moving so slowly that ants marched faster. One morning, a curious toucan dropped a shiny berry. Sid, intrigued, reached for it over hours, only to find it was a pebble! Chuckling, he napped, dreaming of sweeter finds. His unhurried life taught the jungle: patience brings its own rewards. (376 characters)
-
 @ ecda4328:1278f072
2025-05-19 14:41:48
@ ecda4328:1278f072
2025-05-19 14:41:48An honest response to objections — and an answer to the most important question: why does any of this matter?
\ Statement: Deflation is not the enemy, but a natural state in an age of technological progress.\ Criticism: in real macroeconomics, long-term deflation is linked to depressions.\ Deflation discourages borrowers and investors, and makes debt heavier.\ Natural ≠ Safe.
1. “Deflation → Depression, Debt → Heavier”
This is true in a debt-based system. Yes, in a fiat economy, debt balloons to the sky, and without inflation it collapses.
But Bitcoin offers not “deflation for its own sake,” but an environment where you don’t need to be in debt to survive. Where savings don’t melt away.\ Jeff Booth said it clearly:
“Technology is inherently deflationary. Fighting deflation with the printing press is fighting progress.”
You don’t have to take on credit to live in this system. Which means — deflation is not an enemy, but an ally.
💡 People often confuse two concepts:
-
That deflation doesn’t work in an economy built on credit and leverage — that’s true.
-
That deflation itself is bad — that’s a myth.
📉 In reality, deflation is the natural state of a free market when technology makes everything cheaper.
Historical example:\ In the U.S., from the Civil War to the early 1900s, the economy experienced gentle deflation — alongside economic growth, employment expansion, and industrial boom.\ Prices fell: for example, a sack of flour cost \~$1.00 in 1865 and \~$0.50 in 1895 — and there was no crisis, because wages held and productivity increased.
Modern example:\ Consumer electronics over the past 20–30 years are a vivid example of technological deflation:\ – What cost $5,000 in 2000 (e.g., a 720p plasma TV) now costs $300 and delivers 10× better quality.\ – Phones, computers, cameras — all became far more powerful and cheaper at the same time.\ That’s how tech-driven deflation works: you get more for less.
📌 Bitcoin doesn’t make the world deflationary. It just doesn’t fight against deflation, unlike the fiat model that fights to preserve its debt pyramid.\ It stops punishing savers and rewards long-term thinkers.
Even economists often confuse organic tech deflation with crisis-driven (debt) deflation.
\ \ Statement: We’ve never lived in a truly free market — central banks and issuance always existed.\ Criticism: ideological statement.\ A truly “free” market is utopian.\ Banks and monetary issuance emerged in response to crises.\ A market without arbiters is not always fair, especially under imperfect competition.
2. “The Free Market Is a Utopia”
Yes, “pure markets” are rare. But what we have today isn’t regulation — it’s centralized power in the hands of central banks and cartels.
Bitcoin offers rules without rulers. 21 million. No one can change the issuance. It’s not ideology — it’s code instead of trust. And it has worked for 15 years.
\ \ Statement: Inflation is an invisible tax, especially on the poor and working class.\ Criticism: partly true: inflation can reduce debt burden, boost employment.\ The state indexes social benefits. Under stable inflation, compensators can work. Under deflation, things might be worse (mass layoffs, defaults).
3. “Inflation Can Help”
Theoretically — yes. Textbooks say moderate inflation can reduce debt burdens and stimulate consumption and jobs.\ But in practice — it works as a stealth tax, especially on those without assets. The wealthy escape — into real estate, stocks, funds.\ But the poor and working class lose purchasing power because their money is held in cash — and cash devalues.
💬 As Lyn Alden says:
“When your money can’t hold value, you’re forced to become an investor — even if you just want to save and live.”
The state may index pensions or benefits — but always with a lag, and always less than actual price increases.\ If bread rises 15% and your payment increase is 5%, you got poorer, even if the number on paper went up.
💥 We live in an inflationary system of everything:\ – Inflationary money\ – Inflationary products\ – Inflationary content\ – And now even inflationary minds
🧠 This is more than just rising prices — it’s a degradation of reality perception. You’re always rushing, everything loses meaning.\ But when did the system start working against you?
📉 What went wrong after 1971?
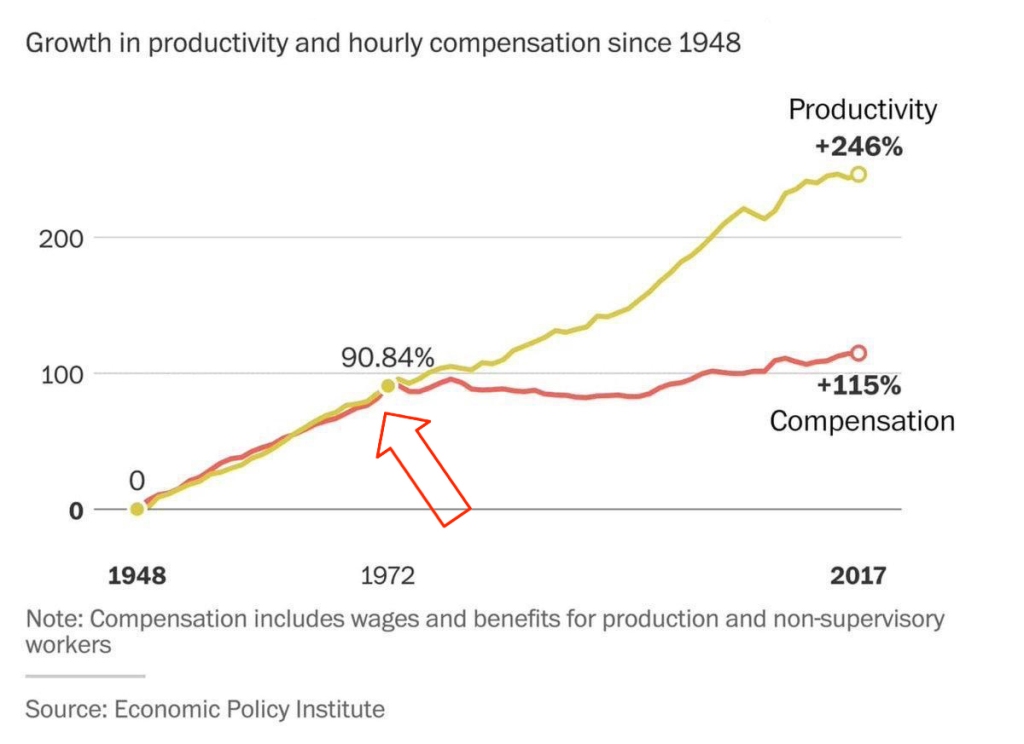 This chart shows that from 1948 to the early 1970s, productivity and wages grew together.\
But after the end of the gold standard in 1971 — the connection broke. Productivity kept rising, but real wages stalled.
This chart shows that from 1948 to the early 1970s, productivity and wages grew together.\
But after the end of the gold standard in 1971 — the connection broke. Productivity kept rising, but real wages stalled.👉 This means: you work more, better, faster — but buy less.
🔗 Source: wtfhappenedin1971.com
When you must spend today because tomorrow it’ll be worth less — that’s rewarding impulse and punishing long-term thinking.
Bitcoin offers a different environment:\ – Savings work\ – Long-term thinking is rewarded\ – The price of the future is calculated, not forced by a printing press
📌 Inflation can be a tool. But in government hands, it became a weapon — a slow, inevitable upward redistribution of wealth.
Indexing is weak compensation if bread is up 15% and your “increase” is only 5%.
\ \ Statement: War is not growth, but a reallocation of resources into destruction.
Criticism: war can spur technological leaps (Internet, GPS, nuclear energy — all from military programs). "Military Keynesianism" was a real model.
4. “War Drives R&D”
Yes, wars sometimes give rise to tech spin-offs: Internet, GPS, nuclear power — all originated from military programs.
But that doesn’t make war a source of progress — it makes tech a byproduct of catastrophe.
“War reallocates resources toward destruction — not growth.”
Progress doesn’t happen because of war — it happens despite it.
If scientific breakthroughs require a million dead and burnt cities — maybe you’ve built your economy wrong.
💬 Even Michael Saylor said:
“If you need war to develop technology — you’ve built civilization wrong.”
No innovation justifies diverting human labor, minds, and resources toward destruction.\ War is always the opposite of efficiency — more is wasted than created.
🧠 Bitcoin, on the other hand, is an example of how real R&D happens without violence.\ No taxes. No army. Just math, voluntary participation, and open-source code.
📌 Military Keynesianism is not a model of progress — it’s a symptom of a sick monetary system that needs destruction to reboot.
Bitcoin shows that coordination without violence is possible.\ This is R&D of a new kind: based not on destruction, but digital creation.
Statement: Bitcoin isn’t “Gold 1.0,” but an improved version: divisible, verifiable, unseizable.
Criticism: Bitcoin has no physical value; "unseizability" is a theory;\ Gold is material and autonomous.
5. “Bitcoin Has No Physical Value”
And gold does? Just because it shines?
Physical form is no guarantee of value.\ Real value lies in: scarcity, reliable transfer, verifiability, and non-confiscatability.
Gold is:\ – Hard to divide\ – Hard to verify\ – Expensive to store\ – Easy to seize
💡 Bitcoin is the first store of value in history that is fully free from physical limitations, and yet:\ – Absolutely scarce (21M, forever)\ – Instantly transferable over the Internet\ – Cryptographically verifiable\ – Controlled by no government
🔑 Bitcoin’s value lies in its liberation from the physical.\ It doesn’t need to be “backed” by gold or oil. It’s backed by energy, mathematics, and ongoing verification.
“Price is what you pay, value is what you get.” — Warren Buffett
When you buy bitcoin, you’re not paying for a “token” — you’re gaining access to a network of distributed financial energy.
⚡️ What are you really getting when you own bitcoin?\ – A key to a digital asset that can’t be faked\ – The ability to send “crystallized energy” anywhere on Earth\ – A role in a new accounting system that runs 24/7/365\ – Freedom: from banks, borders, inflation, and force
📉 Bitcoin doesn’t require physical value — because it creates value:\ Through trust, scarcity, and energy invested in mining.\ And unlike gold, it was never associated with slavery.
Statement: There’s no “income without risk” in Bitcoin: just hold — you preserve; want more — invest, risk, build.
Criticism: contradicts HODL logic; speculation remains dominant behavior.
6. “Speculation Dominates”
For now — yes. That’s normal for the early phase of a new technology. Awareness doesn’t come instantly.
What matters is not the motive of today’s buyer — but what they’re buying.
📉 A speculator may come and go — but the asset remains.\ And this asset is the only one in history that will never exist again. 21 million. Forever.
📌 Look deeper. Bitcoin has:\ – No CEO\ – No central issuer\ – No inflation\ – No “off switch”
💡 It’s not a stock. Not a startup. Not someone’s project.\ It’s a new foundation for trust.\ It’s opting out of a system where freedom is a privilege you’re granted under conditions.
🧠 People say: “Bitcoin can be copied.”\ Theoretically — yes.\ Practically — never.
Here’s what you’d need to recreate Bitcoin:\ – No pre-mine\ – A founder who disappears and never sells\ – No foundation or corporation\ – Tens of thousands of nodes worldwide\ – 701 million terahashes of hash power\ – Thousands of devs writing open protocols\ – Hundreds of global conferences\ – Millions of people defending digital sovereignty\ – All that without a single marketing budget
That’s all.
🔁 Everything else is an imitation, not a creation.\ Just like you can’t “reinvent fire” — Bitcoin can only exist once.
Statements:\ The Russia's '90s weren’t a free market — just anarchic chaos without rights protection.*\ Unlike fiat or even dollars, Bitcoin is the first asset with real defense — from governments, inflation, even thugs.\ And yes, even if your barber asks about Bitcoin — maybe it's not a bubble, but a sign that inflation has already hit everyone.
Criticism: Bitcoin’s protection isn’t universal — it works only with proper handling and isn’t available to all.\ Some just want to “get rich.”\ None of this matters because:
-
Bitcoin’s volatility (-30% in a week, +50% in a month) makes it unusable for price planning or contracts.
-
It can’t handle mass-scale usage.
-
To become currency, geopolitical will is needed — and without the first two, don’t even talk about the third.\ Also: “Bitcoin is too complicated for the average person.”
7. “It’s Too Complex for the Masses”
It’s complex — if you’re using L1 (Layer 1). But even grandmas use Telegram. In El Salvador, schoolkids buy lunch with Lightning. My barber installed Wallet of Satoshi in minutes right in front of me — and I now pay for my haircut via Lightning.
UX is just a matter of time. And it’s improving. Emerging tools:\ Cashu, Fedimint, Fedi, Wallet of Satoshi, Phoenix, Proton Wallet, Swiss Bitcoin Pay, Bolt Card / CoinCorner (NFC cards for Lightning payments).
This is like the internet in 1995:\ It started with modems — now it’s 4K streaming.
8. “Can’t Handle the Load”
A common myth.\ Yes, Bitcoin L1 processes about 7 transactions per second — intentionally. It’s not built to be Visa. It’s a financial protocol, just like TCP/IP is a network protocol. TCP/IP isn’t “fast” or “slow” — the experience depends on the infrastructure built on top: servers, routers, hardware. In the ’90s, it delivered text. Today, it streams Netflix. The protocol didn’t change — the stack did.
Same with Bitcoin: L1 defines rules, security, finality.\ Scaling and speed? That’s the second layer’s job.
To understand scale:
| Network | TPS (Transactions/sec) | | --- | --- | | Visa | up to 24,000 | | Mastercard | \~5,000 | | PayPal | \~193 | | Litecoin | \~56 | | Ethereum | \~20 | | Bitcoin | \~7 |
\ ⚡️ Enter Lightning Network — Bitcoin’s “fast lane.”\ It allows millions of transactions per second, instantly and nearly free.
And it’s not a sidechain.
❗️ Lightning is not a separate network.\ It uses real Bitcoin transactions (2-of-2 multisig). You can close the channel to L1 at any time. It’s not an alternative — it’s a native extension built into Bitcoin.\ Also evolving: Ark, Fedimint, eCash — new ways to scale and add privacy.
📉 So criticizing Bitcoin for “slowness” is like blaming TCP/IP because your old modem won’t stream YouTube.\ The protocol isn’t the problem — it’s the infrastructure.
🛡️ And by the way: Visa crashes more often than Bitcoin.
9. “We Need Geopolitical Will”
Not necessarily. All it takes is the will of the people — and leaders willing to act. El Salvador didn’t wait for G20 approval or IMF blessings. Since 2001, the country had used the US dollar as its official currency, abandoning its own colón. But that didn’t save it from inflation or dependency on foreign monetary policy. In 2021, El Salvador became the first country to recognize Bitcoin as legal tender. Since March 13, 2024, they’ve been purchasing 1 BTC daily, tracked through their public address:
🔗 Address\ 📅 First transaction
This policy became the foundation of their Strategic Bitcoin Reserve (SBR) — a state-led effort to accumulate Bitcoin as a national reserve asset for long-term stability and sovereignty.
Their example inspired others.
In March 2025, U.S. President Donald Trump signed an executive order creating the Strategic Bitcoin Reserve of the USA, to be funded through confiscated Bitcoin and digital assets.\ The idea: accumulate, don’t sell, and strategically expand the reserve — without extra burden on taxpayers.
Additionally, Senator Cynthia Lummis (Wyoming) proposed the BITCOIN Act, targeting the purchase of 1 million BTC over five years (\~5% of the total supply).\ The plan: fund it via revaluation of gold certificates and other budget-neutral strategies.
📚 More: Strategic Bitcoin Reserve — Wikipedia
👉 So no global consensus is required. No IMF greenlight.\ All it takes is conviction — and an understanding that the future of finance lies in decentralized, scarce assets like Bitcoin.
10. “-30% in a week, +50% in a month = not money”
True — Bitcoin is volatile. But that’s normal for new technologies and emerging money. It’s not a bug — it’s a price discovery phase. The world is still learning what this asset is.
📉 Volatility is the price of entry.\ 📈 But the reward is buying the future at a discount.
As Michael Saylor put it:
“A tourist sees Niagara Falls as chaos — roaring, foaming, spraying water.\ An engineer sees immense energy.\ It all depends on your mental model.”
Same with Bitcoin. Speculators see chaos. Investors see structural scarcity. Builders see a new financial foundation.
💡 Now consider gold:
👉 After the U.S. abandoned the gold standard in 1971, gold surged from \~$35 to over $800 in a decade — while suffering wild -40% to -60% crashes along the way.\ \ 📈 Gold Price Chart — Macrotrends\ \ Nobody said, “This can’t be money.” \ Because money is defined not by volatility, but by scarcity, adoption, and trust — which build over time.
📊 The more people save in Bitcoin, the more its volatility fades.
This is a journey — not a fixed state.
We don’t judge the internet by how it worked in 1994.\ So why expect Bitcoin to be the “perfect currency” in 2025?
It grows bottom-up — without regulators’ permission.\ And the longer it survives, the stronger it becomes.
Remember how many times it’s been declared dead.\ And how many times it came back — stronger.
📊 Gold vs. Bitcoin: Supply Comparison
This chart shows the key difference between the two hard assets:
🔹 Gold — supply keeps growing.\ Mining may be limited, but it’s still inflationary.\ Each year, there’s more — with no known cap: new mines, asteroid mining, recycling.
🔸 Bitcoin — capped at 21 million.\ The emission schedule is public, mathematically predictable, and ends completely around 2140.
🧠 Bottom line:\ Gold is good.\ Bitcoin is better — for predictability and scarcity.
💡 As Saifedean Ammous said:
“Gold was the best monetary good… until Bitcoin.”
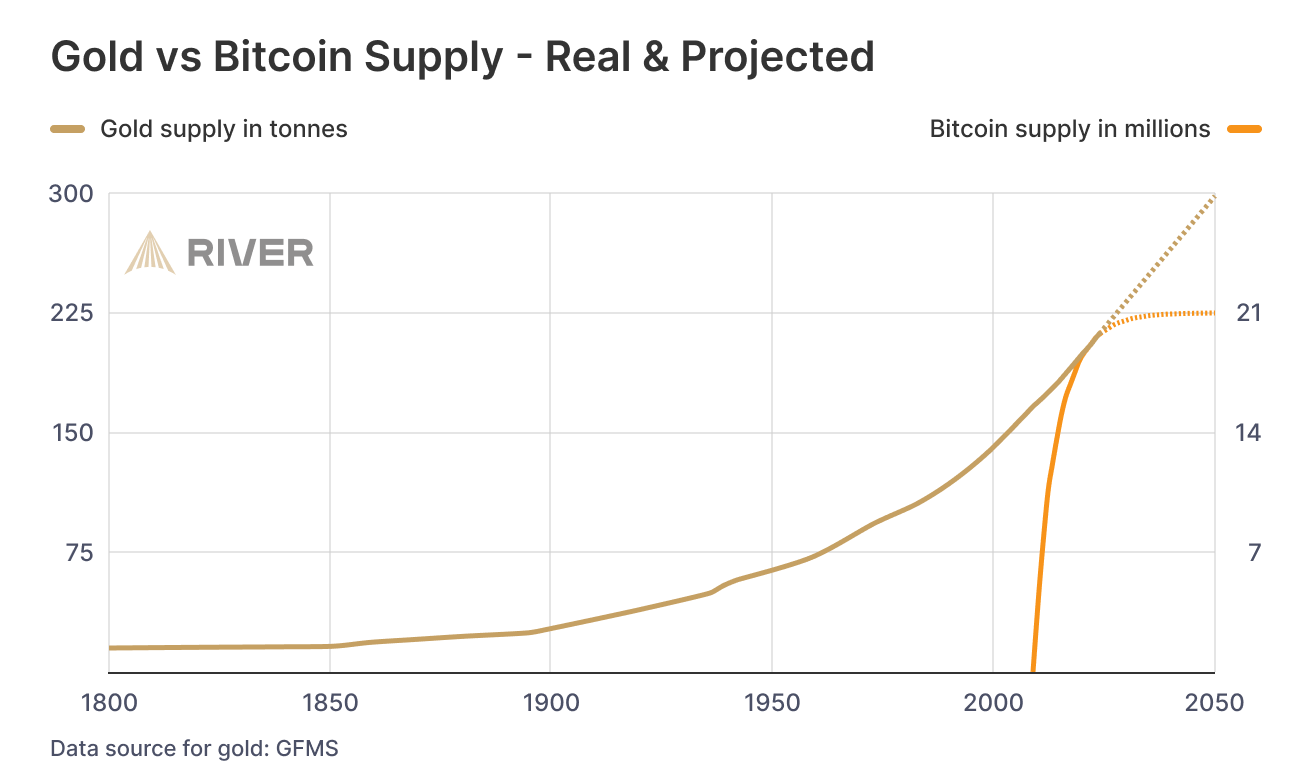
While we argue — fiat erodes every day.
No matter your view on Bitcoin, just show me one other asset that is simultaneously:
– immune to devaluation by decree\ – impossible to print more of\ – impossible to confiscate by a centralized order\ – impossible to counterfeit\ – and, most importantly — transferable across borders without asking permission from a bank, a state, or a passport
💸 Try sending $10,000 through PayPal from Iran to Paraguay, or Bangladesh to Saint Lucia.\ Good luck. PayPal doesn't even work there.
Now open a laptop, type 12 words — and you have access to your savings anywhere on Earth.
🌍 Bitcoin doesn't ask for permission.\ It works for everyone, everywhere, all the time.
📌 There has never been anything like this before.
Bitcoin is the first asset in history that combines:
– digital nature\ – predictable scarcity\ – absolute portability\ – and immunity from tyranny
💡 As Michael Saylor said:
“Bitcoin is the first money in human history not created by bankers or politicians — but by engineers.”
You can own it with no bank.\ No intermediary.\ No passport.\ No approval.
That’s why Bitcoin isn’t just “internet money” or “crypto” or “digital gold.”\ It may not be perfect — but it’s incorruptible.\ And it’s not going away.\ It’s already here.\ It is the foundation of a new financial reality.
🔒 This is not speculation. This is a peaceful financial revolution.\ 🪙 This is not a stock. It’s money — like the world has never seen.\ ⛓️ This is not a fad. It’s a freedom protocol.
And when even the barber starts asking about Bitcoin — it’s not a bubble.\ It’s a sign that the system is breaking.\ And people are looking for an exit.
For the first time — they have one.
💼 This is not about investing. It’s about the dignity of work.
Imagine a man who cleans toilets at an airport every day.
Not a “prestigious” job.\ But a crucial one.\ Without him — filth, bacteria, disease.
He shows up on time. He works with his hands.
And his money? It devalues. Every day.
He doesn’t work less — often he works more than those in suits.\ But he can afford less and less — because in this system, honest labor loses value each year.
Now imagine he’s paid in Bitcoin.
Not in some “volatile coin,” but in hard money — with a limited supply.\ Money that can’t be printed, reversed, or devalued by central banks.
💡 Then he could:
– Stop rushing to spend, knowing his labor won’t be worth less tomorrow\ – Save for a dream — without fear of inflation eating it away\ – Feel that his time and effort are respected — because they retain value
Bitcoin gives anyone — engineer or janitor — a way out of the game rigged against them.\ A chance to finally build a future where savings are real.
This is economic justice.\ This is digital dignity.
📉 In fiat, you have to spend — or your money melts.\ 📈 In Bitcoin, you choose when to spend — because it’s up to you.
🧠 In a deflationary economy, both saving and spending are healthy:
You don’t scramble to survive — you choose to create.
🎯 That’s true freedom.
When even someone cleaning floors can live without fear —\ and know that their time doesn’t vanish... it turns into value.
-
-
 @ a5ee4475:2ca75401
2025-05-18 16:07:07
@ a5ee4475:2ca75401
2025-05-18 16:07:07ai #artificial #intelligence #english #tech
Open Source
Models
Text
Image
- SDAI FOSS - Stable Diffusion AI to Android [download] [source] 🤖
- Stable Diffusion - Text to image [source] 🌐
- Pixart Alpha - Photorealistic Text to Image Generation [source]
- Pixart Delta - Framework to Pixart Alpha [paper] [source]
- Pixart Sigma - 4K Text to Image Generation [source]
- OmniGen - Pompt, image or subject to image [source]
- Pigallery - Self-Hosted AI Image Generator [source]
Video
Tools
Lightning Based
- Animal Sunset - AI video generation with Nostr npub by lightning payments [source]
- Ai Rand - AI text generation with Pubky DNS by lightning payments [source]
- PlebAI - Text and Image generation without signup [source] 🌐🤖🍎 [sites down - only github available]
Others
- HuggingFace - Test and collaborate on models, datasets and apps. [source]
- DuckDuckGo AI Chat - Famous AIs without Login [source]
- Ollama - Run LLMs Locally [source]
- DreamStudio - Stable Diffusion’s Web App Tool [info] [source]
- Prompt Gallery - AI images with their prompts [source]
Closed Source
Models
Text
- ChatGPT
- Claude
- Gemini
- Copilot
- Maritalk - Text AI in Portuguese focused on Brazil with model Sabia-3 and the open source models Sabia-7b and Sabia-2 [source]
- Amazônia IA - Text AI in Portuguese focused on Brazil with the guara, hapia and golia models [source]
Image
Video
- Minimax - Realistic videos (prompts only in chinese)
Tools
Other index: Amazing AI
-
 @ fbe736db:187bb0d5
2025-05-18 14:25:49
@ fbe736db:187bb0d5
2025-05-18 14:25:49This article was published in November 2024 by the Bitcoin Collective and is best viewed here for images
Ssssh. Did you hear that? In their recent Q3 2024 earnings call MicroStrategy (NSQ:MSTR) announced plans to buy a further $42 billion worth of Bitcoin over the next 3 calendar years. Here are some reflections on where MicroStrategy has come from, and where they are going.
From the beginning
Let’s rewind as to how we got here. Microstrategy is a business intelligence software company originally founded by Michael Saylor in 1989.
They started acquiring Bitcoin in Q3 2020, firstly via their cash reserves on the balance sheet. This was soon followed by debt issuance (mainly in the form of convertible debt), and has in more recent years been followed by issuing further MSTR equity into the market, alongside yet more convertible debt issuance.
Nearly all the proceeds have gone towards buying bitcoin. As can be seen on the chart below, they have managed to steadily grow these holdings, albeit this growth visibly slowed in the last bear market.
[p13 of Q3 2024 Earnings Presentation. Please note - all screenshots from this article come from the slide deck accompanying the recent MSTR Q3 earnings presentation, which can be viewed by clicking here]
MSTR now holds well over 1% of all the Bitcoin that will ever exist. With Bitcoin nearing all time highs again, this Bitcoin is worth around $18.3bn at the time of writing, and has an average purchase cost of around $9.9bn.
This has led to a spectacular share price performance, unmatched in the entire S&P 500 since August 2020.
[p23 of Q3 2024 Earnings Presentation]
It was not always this way. When I wrote this article in July 2022, MSTR was firmly in the red and sitting on unrealised bitcoin losses of $1.4bn. A search for Michael Saylor on Twitter back then auto-completed to “Michael Saylor liquidated”.
Rumours of imminent demise were always unfounded since the debt was of long enough term, and with the exception of a small proportion, could not be margin called.
A developing strategy
What’s interesting about MicroStrategy since then is their developing vision as to how to add Bitcoin to their balance sheet and more value to shareholders. This is especially in terms of outperforming BTC and achieving what they define as a “positive BTC yield” – not yield in a conventional sense but a measure of increasing the number of bitcoin held per assumed diluted shares outstanding.
The concept of MSTR outperforming bitcoin is interesting to me, as I’ve previously suggested attempting to value MSTR stock as priced in bitcoin rather than dollars. This then begs the question of whether an investment of bitcoin into MSTR shares will positively perform in bitcoin terms over time.
This valuation is very difficult by its nature, but can broadly be done by adding the bitcoin they currently hold on their balance sheet with an estimate of all the bitcoin they may ever acquire in the future, plus an allowance for other factors such as debt.
The landscape has shifted over this period, with Michael Saylor admitting that their strategy has evolved over time. The vital point that I missed when considering how MSTR might acquire more bitcoin in the future was their ability to issue considerable amounts of new equity into the market and achieve two things in doing so:
i) increasing bitcoin held per share of existing shareholders
ii) strengthen their balance sheet to take on more debt (since further debt issued would be a smaller proportion of their overall balance sheet).
“But where does the (btc) yield come from?”
This is not yield in the conventional sense, but nor is it Terra Luna. Firstly, this could come from profits from the business, which are relatively small. More relevantly, let’s consider how both the capital raises from debt and equity have served to increase the bitcoin held per share.
1. Equity “at the money” offerings
Much has been made of MSTR’s market cap (i.e. the overall value of the shares) trading above “Net Asset Value” (NAV) – which is essentially the value of their current bitcoin holdings plus the value of the conventional business, less debt. A multiple approach is used to describe how far above or below NAV this might be.
At the time of writing, the MSTR market cap stands at around $50bn and the value of their bitcoin holdings at $18bn. Given the conventional MSTR business is relatively small, it’s easy to see how this is approaching a multiple of 3x NAV.
If the share price is $240 and the net asset value is only $80 per share, MSTR can then issue more equity at $240, buy more bitcoin with this, and by doing so increase the bitcoin per share of existing shareholders. What’s more, they can keep doing this as long as the share price remains high. As shown above, MSTR has coined the term “BTC yield” to measure how well they are performing at increasing bitcoin held per share.
2. Convertible Debt
This also generally serves to increase bitcoin held per share. To consider how, let’s consider one of the previous convertible debt offerings – those due in 2028 – works in practice
Amount borrowed – $1,010m
Annual interest rate payable – 0.625%
Conversion price – $183.2
As can see MSTR pays a very low interest rate, as most of the value of the bond is in the potential convertibility to MSTR equity at a price of $183.2. Ultimately there is a binary situation here – either the share price is above that level and they end up issuing more equity at that price, or it’s below, and they end up having simply borrowed money at a very low interest rate.
The crucial point is that the convertible bond conversion price is typically set at a premium of at least 30% to the current market share price, whilst MSTR are buying bitcoin at the outset with the bond proceeds.
Hence if all of this debt converts to equity (and all debt looks like it will at present – see slide below), they are typically managing to increase the BTC held per share for existing shareholders.
This is because in this example when the bonds are converted to shares at $183.2, this is done at a premium to the prior share price (let’s say for illustration it was $140) at which MSTR initially issued the debt and converted the borrowing proceeds to bitcoin.
[p16 of Q3 2024 Earnings Presentation]
It is these combined activities that have led to an impressive bitcoin yield of 17.8% for the year to date 2024, and leads to questions for how long this financial alchemy can continue. Some bitcoiners, such as the Quant Bros duo and True North* group (see both here) have spoken of a flywheel effect – the more Bitcoin MSTR can acquire and the higher the bitcoin per share metric goes, the higher the share price, which in turn increases their ability to issue yet more equity and debt to buy more bitcoin and further increase bitcoin per share.
*Side note – Michael Saylor used the phrase “True North” on the Earnings Call; likely not accidental.
One answer to how long this can continue is – as long as the equity and debt markets still show an appetite for snapping up the new debt and equity issuance, even if the share price is high. Michael Saylor characterises it as the beginning of the adoption of Bitcoin as digital capital for these markets, and MSTR constitutes the easiest exposure. They have established a monopoly of sorts – whilst it would feasibly be possible for a large company to catch them in Bitcoin held, it would still have a smaller proportion of its business exposed to Bitcoin than MSTR.
[p21 of Q3 2024 Earnings Presentation]
Volatility is vitality
Michael Saylor is very clear in this earnings call and other interviews that MicroStrategy’s share volatility is a feature and not a bug. It is more volatile than any other S&P stock. As can be seen below, the recent daily trading volume only trails to the very biggest companies in the S&P 500.
Saylor embraces this volatility. It is what gives the optionality component of their convertible debt its value, and allows the interest rate payable to be lower. In addition, when the share price is high MSTR can issue more equity and increase bitcoin per share.
The Earnings presentation makes reference to several different forms of Bitcoin exposure that MSTR can offer to the market now and in the future.
[p27 of Q3 2024 Earnings Presentation]
The MSTR “True North” Principles
The Q3 Earnings call saw the following principles outlined for the first time. The message is clear to the market – do not conflate the dollar volatility of MSTR’s share price with the nature of their Bitcoin principles, which (perhaps analogous to the Bitcoin protocol itself) are intended to be rock solid and consistent. In addition, Saylor cleared up one source of speculation – MSTR will not be seeking to purchase other companies to add to its potential for generating free cash flows to invest into Bitcoin.
[p34 of Q3 2024 Earnings Presentation]
Can’t stop, won’t stop
The Earnings call contained an ambitious plan to raise $42bn more capital over the next 3 calendar years. This would be $21bn worth of equity, by selling new shares into the market (known as an “at the money” equity option), and $21bn worth of fixed income debt. This was split as $10bn in 2025, $14bn in 2026 and $18bn in 2027.
There is no doubting the scale of this ambition – to date MSTR have issued in total around $4.3bn in convertible debt and $4.3bn in terms of issued equity.
One key point is clear in line with the principles listed above. Whilst Saylor wants to raise Capital at opportune times to best benefit shareholders in the long term and to achieve what he terms “intelligent leverage”, he doesn’t try and time his bitcoin buys.
Moreover, he is likely also not bothered that selling so much further equity into the market may not always benefit the share price in the short term.
[p33 of Q3 2024 Earnings Presentation]
Turning up the volume, but is anyone listening?
With this announcement of $42bn to come over the next 3 years, there is no end in sight with respect to MSTR’s thirst for further Bitcoin purchases.
And yet, there was little in the media around the announcement, and despite the share price performance topping the entire S&P 500 over the past 4 years, MicroStrategy sits nowhere on Google Trends in comparison to Bitcoin:
[Source: https://trends.google.co.uk/trends/explore?q=bitcoin,microstrategy&hl=en-GB]
For now, this is no Gamestop. There’s no huge amount of short interest, and the fabled retail crowds are nowhere to be seen. One thing’s for sure though. Buckle up.
Please get in touch with your thoughts and feedback.
-
 @ cefb08d1:f419beff
2025-05-19 11:38:06
@ cefb08d1:f419beff
2025-05-19 11:38:06Source : https://mymodernmet.com/2024-dog-photography-awards/
https://stacker.news/items/983647
-
 @ cefb08d1:f419beff
2025-05-19 07:13:51
@ cefb08d1:f419beff
2025-05-19 07:13:51https://stacker.news/items/983539
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-19 00:31:55
@ 5d4b6c8d:8a1c1ee3
2025-05-19 00:31:55We have our conference finalists: - Indiana (4) @ New York (3) - Minnesota (6) @ OKC (1)
Pick one team to advance to the finals and one player to win Conference Finals MVP. One player from each matchup will be named MVP.
The scoring this round is 4 points + seed value for picking a winner and 4 points for picking an MVP. The maximum points this round are 14.
Current Scores | Stacker | Points | |----------|-------| | @Undisciplined | 35 | | @grayruby | 32 | | @gnilma | 28 | | @fishious | 21 | | @WeAreAllSatoshi | 20 | | @BlokchainB | 19 | | @Coinsreporter | 19 | | @Carresan | 18 | | @Car | 9 |
SGA was the leading scorer of round 2
https://stacker.news/items/983402
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-18 16:24:01
@ 5d4b6c8d:8a1c1ee3
2025-05-18 16:24:01First, the caveat: Yes, I understand that there's a consistent libertarian case for free trade as a policy position.
With all the discourse around tariffs, I wanted to highlight something of a moral oddity in the arguments being used by many free trade libertarians (I am a free trade libertarian, btw): namely, the idea that we (Americans) should happily take advantage of subsidized exports from poorer countries.
I do agree with the economics of the argument: By subsidizing exports, other countries are imposing a deadweight loss on themselves and passing savings along to US consumers.
Why are libertarians celebrating this, though? Poor, oppressed foreigners are being stolen from by their authoritarian governments and American consumers are benefiting from it financially. Thinking this is a good situation is odd and thinking you have a right to take part in it is even stranger.
Libertarians certainly understand that subsidies are wrong and economically harmful, and that they benefit a select group of politically connected cronies. Nothing about that changes just because it's happening in a foreign country and your grocery bill benefits from it.
Saying "That's how they run their country. It's none of our business." is a plea to moral relativism, which libertarians generally avoid. Libertarians also usually understand that the "they" who rule is not the same as the "they" who are ruled. Is it just too uncomfortable to acknowledge being the beneficiary of abuse?
I can't help but draw parallels to the abolitionists of two hundred years ago, who refused to buy the products of slaves. I think they're mostly viewed as having been "on the right side of history", but they're probably on the "wrong" side of most "free trade" arguments. Another of those arguments being that it doesn't help the poor oppressed foreigner to stop doing business with their oppressor (yes, many lefties get all mixed up about who the oppressors are).
Anyway, I have no brilliant conclusion to offer. What do you all think?
https://stacker.news/items/983054
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-18 14:42:48
@ 5d4b6c8d:8a1c1ee3
2025-05-18 14:42:48What do we mean when we talk about "fitness"? The word implies a connection to a higher purpose: "Fitness for what?"
Biologically, "fitness" refers to the propensity of an organism to pass on it's genes. Biological fitness is clearly context dependent: i.e. an anaconda isn't so fit if it gets moved to the arctic. I think we can build on that, while making it more human.
I think of fitness as our capacity to thrive in our environment. That's going to be different for each of us, depending on our environment and our preferences. However, there are some useful implications of thinking of fitness this way: 1. Chores, errands, work, play, and family activities might be the best kind of exercise, since they are physical activities that are directly tied to your lifestyle. 2. Supplemental exercise should be geared towards your lifestyle and improving your ability to accomplish things you need to be able to do. 3. There's no such thing as a universal "best exercise" or "best diet", because we all have different fitness objectives. 4. "Fitness" is not static: We do different things and have different priorities at different points in our lives, so our fitness goals should change over time. Many of us will even have seasonal fitness changes, since we don't do the same things in winter as we do in summer.
How do you all think about "fitness"?
Is it a highfalutin ivory tower concept or is it just ABs?
https://stacker.news/items/982981