-
 @ 5d4b6c8d:8a1c1ee3
2025-05-20 00:09:55
@ 5d4b6c8d:8a1c1ee3
2025-05-20 00:09:55https://youtu.be/EPiE-Ruhohg
I'm pretty sure Ben called Caruso the "Bald Mamba" in this video, which is an awesome nickname for him.
Great walkthrough of the adjustments made over the course of seven games to try to disrupt Joker, culminating with putting Caruso (who's 100 lbs lighter and 6 inches shorter) on him.
https://stacker.news/items/984227
-
 @ 3f770d65:7a745b24
2025-05-19 18:09:52
@ 3f770d65:7a745b24
2025-05-19 18:09:52🏌️ Monday, May 26 – Bitcoin Golf Championship & Kickoff Party
Location: Las Vegas, Nevada\ Event: 2nd Annual Bitcoin Golf Championship & Kick Off Party"\ Where: Bali Hai Golf Clubhouse, 5160 S Las Vegas Blvd, Las Vegas, NV 89119\ 🎟️ Get Tickets!
Details:
-
The week tees off in style with the Bitcoin Golf Championship. Swing clubs by day and swing to music by night.
-
Live performances from Nostr-powered acts courtesy of Tunestr, including Ainsley Costello and others.
-
Stop by the Purple Pill Booth hosted by Derek and Tanja, who will be on-boarding golfers and attendees to the decentralized social future with Nostr.
💬 May 27–29 – Bitcoin 2025 Conference at the Las Vegas Convention Center
Location: The Venetian Resort\ Main Attraction for Nostr Fans: The Nostr Lounge\ When: All day, Tuesday through Thursday\ Where: Right outside the Open Source Stage\ 🎟️ Get Tickets!
Come chill at the Nostr Lounge, your home base for all things decentralized social. With seating for \~50, comfy couches, high-tops, and good vibes, it’s the perfect space to meet developers, community leaders, and curious newcomers building the future of censorship-resistant communication.
Bonus: Right across the aisle, you’ll find Shopstr, a decentralized marketplace app built on Nostr. Stop by their booth to explore how peer-to-peer commerce works in a truly open ecosystem.
Daily Highlights at the Lounge:
-
☕️ Hang out casually or sit down for a deeper conversation about the Nostr protocol
-
🔧 1:1 demos from app teams
-
🛍️ Merch available onsite
-
🧠 Impromptu lightning talks
-
🎤 Scheduled Meetups (details below)
🎯 Nostr Lounge Meetups
Wednesday, May 28 @ 1:00 PM
- Damus Meetup: Come meet the team behind Damus, the OG Nostr app for iOS that helped kickstart the social revolution. They'll also be showcasing their new cross-platform app, Notedeck, designed for a more unified Nostr experience across devices. Grab some merch, get a demo, and connect directly with the developers.
Thursday, May 29 @ 1:00 PM
- Primal Meetup: Dive into Primal, the slickest Nostr experience available on web, Android, and iOS. With a built-in wallet, zapping your favorite creators and friends has never been easier. The team will be on-site for hands-on demos, Q\&A, merch giveaways, and deeper discussions on building the social layer of Bitcoin.
🎙️ Nostr Talks at Bitcoin 2025
If you want to hear from the minds building decentralized social, make sure you attend these two official conference sessions:
1. FROSTR Workshop: Multisig Nostr Signing
-
🕚 Time: 11:30 AM – 12:00 PM
-
📅 Date: Wednesday, May 28
-
📍 Location: Developer Zone
-
🎤 Speaker: nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqgdwaehxw309ahx7uewd3hkcqpqs9etjgzjglwlaxdhsveq0qksxyh6xpdpn8ajh69ruetrug957r3qf4ggfm (Austin Kelsay) @ Voltage\ A deep-dive into FROST-based multisig key management for Nostr. Geared toward devs and power users interested in key security.
2. Panel: Decentralizing Social Media
-
🕑 Time: 2:00 PM – 2:30 PM
-
📅 Date: Thursday, May 29
-
📍 Location: Genesis Stage
-
🎙️ Moderator: nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqy08wumn8ghj7mn0wd68yttjv4kxz7fwv3jhyettwfhhxuewd4jsqgxnqajr23msx5malhhcz8paa2t0r70gfjpyncsqx56ztyj2nyyvlq00heps - Bitcoin Strategy @ Roxom TV
-
👥 Speakers:
-
nostr:nprofile1qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcppemhxue69uhkummn9ekx7mp0qqsy2ga7trfetvd3j65m3jptqw9k39wtq2mg85xz2w542p5dhg06e5qmhlpep – Early Bitcoin dev, CEO @ Sirius Business Ltd
-
nostr:nprofile1qy2hwumn8ghj7mn0wd68ytndv9kxjm3wdahxcqg5waehxw309ahx7um5wfekzarkvyhxuet5qqsw4v882mfjhq9u63j08kzyhqzqxqc8tgf740p4nxnk9jdv02u37ncdhu7e3 – Analyst & Partner @ Ego Death Capital
Get the big-picture perspective on why decentralized social matters and how Nostr fits into the future of digital communication.
🌃 NOS VEGAS Meetup & Afterparty
Date: Wednesday, May 28\ Time: 7:00 PM – 1:00 AM\ Location: We All Scream Nightclub, 517 Fremont St., Las Vegas, NV 89101\ 🎟️ Get Tickets!
What to Expect:
-
🎶 Live Music Stage – Featuring Ainsley Costello, Sara Jade, Able James, Martin Groom, Bobby Shell, Jessie Lark, and other V4V artists
-
🪩 DJ Party Deck – With sets by nostr:nprofile1qy0hwumn8ghj7cmgdae82uewd45kketyd9kxwetj9e3k7mf6xs6rgqgcwaehxw309ahx7um5wgh85mm694ek2unk9ehhyecqyq7hpmq75krx2zsywntgtpz5yzwjyg2c7sreardcqmcp0m67xrnkwylzzk4 , nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqgkwaehxw309anx2etywvhxummnw3ezucnpdejqqg967faye3x6fxgnul77ej23l5aew8yj0x2e4a3tq2mkrgzrcvecfsk8xlu3 , and more DJs throwing down
-
🛰️ Live-streamed via Tunestr
-
🧠 Nostr Education – Talks by nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq37amnwvaz7tmwdaehgu3dwfjkccte9ejx2un9ddex7umn9ekk2tcqyqlhwrt96wnkf2w9edgr4cfruchvwkv26q6asdhz4qg08pm6w3djg3c8m4j , nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqg7waehxw309anx2etywvhxummnw3ezucnpdejz7ur0wp6kcctjqqspywh6ulgc0w3k6mwum97m7jkvtxh0lcjr77p9jtlc7f0d27wlxpslwvhau , nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq3vamnwvaz7tmwdaehgu3wd33xgetk9en82m30qqsgqke57uygxl0m8elstq26c4mq2erz3dvdtgxwswwvhdh0xcs04sc4u9p7d , nostr:nprofile1q9z8wumn8ghj7erzx3jkvmmzw4eny6tvw368wdt8da4kxamrdvek76mrwg6rwdngw94k67t3v36k77tev3kx7vn2xa5kjem9dp4hjepwd3hkxctvqyg8wumn8ghj7mn0wd68ytnhd9hx2qpqyaul8k059377u9lsu67de7y637w4jtgeuwcmh5n7788l6xnlnrgssuy4zk , nostr:nprofile1qy28wue69uhnzvpwxqhrqt33xgmn5dfsx5cqz9thwden5te0v4jx2m3wdehhxarj9ekxzmnyqqswavgevxe9gs43vwylumr7h656mu9vxmw4j6qkafc3nefphzpph8ssvcgf8 , and more.
-
🧾 Vendors & Project Booths – Explore new tools and services
-
🔐 Onboarding Stations – Learn how to use Nostr hands-on
-
🐦 Nostrich Flocking – Meet your favorite nyms IRL
-
🍸 Three Full Bars – Two floors of socializing overlooking vibrant Fremont Street
| | | | | ----------- | -------------------- | ------------------- | | Time | Name | Topic | | 7:30-7:50 | Derek | Nostr for Beginners | | 8:00-8:20 | Mark & Paul | Primal | | 8:30-8:50 | Terry | Damus | | 9:00-9:20 | OpenMike and Ainsley | V4V | | 09:30-09:50 | The Space | Space |
This is the after-party of the year for those who love freedom technology and decentralized social community. Don’t miss it.
Final Thoughts
Whether you're there to learn, network, party, or build, Bitcoin 2025 in Las Vegas has a packed week of Nostr-friendly programming. Be sure to catch all the events, visit the Nostr Lounge, and experience the growing decentralized social revolution.
🟣 Find us. Flock with us. Purple pill someone.
-
-
 @ ecda4328:1278f072
2025-05-19 14:41:48
@ ecda4328:1278f072
2025-05-19 14:41:48An honest response to objections — and an answer to the most important question: why does any of this matter?
\ Statement: Deflation is not the enemy, but a natural state in an age of technological progress.\ Criticism: in real macroeconomics, long-term deflation is linked to depressions.\ Deflation discourages borrowers and investors, and makes debt heavier.\ Natural ≠ Safe.
1. “Deflation → Depression, Debt → Heavier”
This is true in a debt-based system. Yes, in a fiat economy, debt balloons to the sky, and without inflation it collapses.
But Bitcoin offers not “deflation for its own sake,” but an environment where you don’t need to be in debt to survive. Where savings don’t melt away.\ Jeff Booth said it clearly:
“Technology is inherently deflationary. Fighting deflation with the printing press is fighting progress.”
You don’t have to take on credit to live in this system. Which means — deflation is not an enemy, but an ally.
💡 People often confuse two concepts:
-
That deflation doesn’t work in an economy built on credit and leverage — that’s true.
-
That deflation itself is bad — that’s a myth.
📉 In reality, deflation is the natural state of a free market when technology makes everything cheaper.
Historical example:\ In the U.S., from the Civil War to the early 1900s, the economy experienced gentle deflation — alongside economic growth, employment expansion, and industrial boom.\ Prices fell: for example, a sack of flour cost \~$1.00 in 1865 and \~$0.50 in 1895 — and there was no crisis, because wages held and productivity increased.
Modern example:\ Consumer electronics over the past 20–30 years are a vivid example of technological deflation:\ – What cost $5,000 in 2000 (e.g., a 720p plasma TV) now costs $300 and delivers 10× better quality.\ – Phones, computers, cameras — all became far more powerful and cheaper at the same time.\ That’s how tech-driven deflation works: you get more for less.
📌 Bitcoin doesn’t make the world deflationary. It just doesn’t fight against deflation, unlike the fiat model that fights to preserve its debt pyramid.\ It stops punishing savers and rewards long-term thinkers.
Even economists often confuse organic tech deflation with crisis-driven (debt) deflation.
\ \ Statement: We’ve never lived in a truly free market — central banks and issuance always existed.\ Criticism: ideological statement.\ A truly “free” market is utopian.\ Banks and monetary issuance emerged in response to crises.\ A market without arbiters is not always fair, especially under imperfect competition.
2. “The Free Market Is a Utopia”
Yes, “pure markets” are rare. But what we have today isn’t regulation — it’s centralized power in the hands of central banks and cartels.
Bitcoin offers rules without rulers. 21 million. No one can change the issuance. It’s not ideology — it’s code instead of trust. And it has worked for 15 years.
\ \ Statement: Inflation is an invisible tax, especially on the poor and working class.\ Criticism: partly true: inflation can reduce debt burden, boost employment.\ The state indexes social benefits. Under stable inflation, compensators can work. Under deflation, things might be worse (mass layoffs, defaults).
3. “Inflation Can Help”
Theoretically — yes. Textbooks say moderate inflation can reduce debt burdens and stimulate consumption and jobs.\ But in practice — it works as a stealth tax, especially on those without assets. The wealthy escape — into real estate, stocks, funds.\ But the poor and working class lose purchasing power because their money is held in cash — and cash devalues.
💬 As Lyn Alden says:
“When your money can’t hold value, you’re forced to become an investor — even if you just want to save and live.”
The state may index pensions or benefits — but always with a lag, and always less than actual price increases.\ If bread rises 15% and your payment increase is 5%, you got poorer, even if the number on paper went up.
💥 We live in an inflationary system of everything:\ – Inflationary money\ – Inflationary products\ – Inflationary content\ – And now even inflationary minds
🧠 This is more than just rising prices — it’s a degradation of reality perception. You’re always rushing, everything loses meaning.\ But when did the system start working against you?
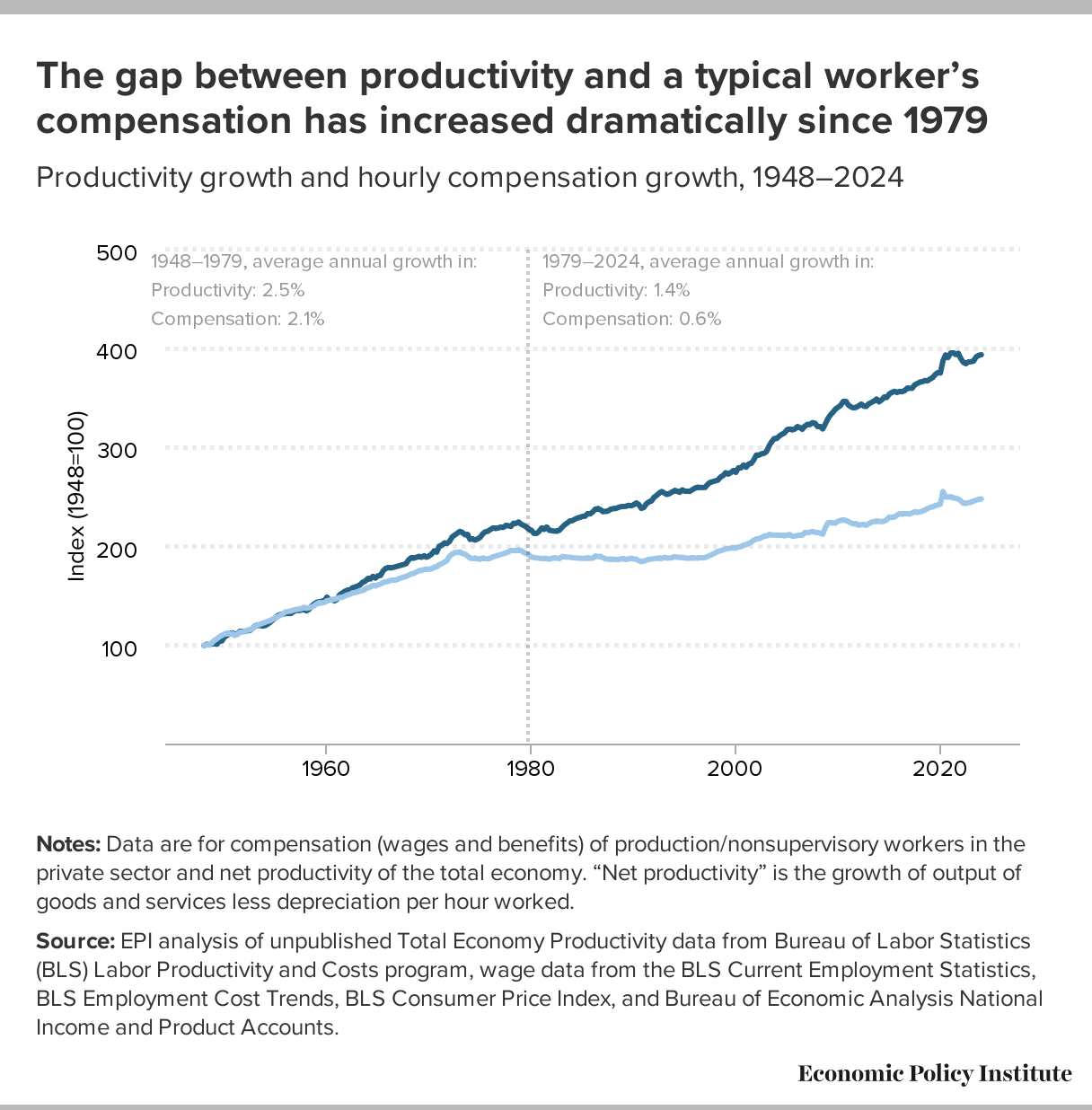
📉 What went wrong after 1971?
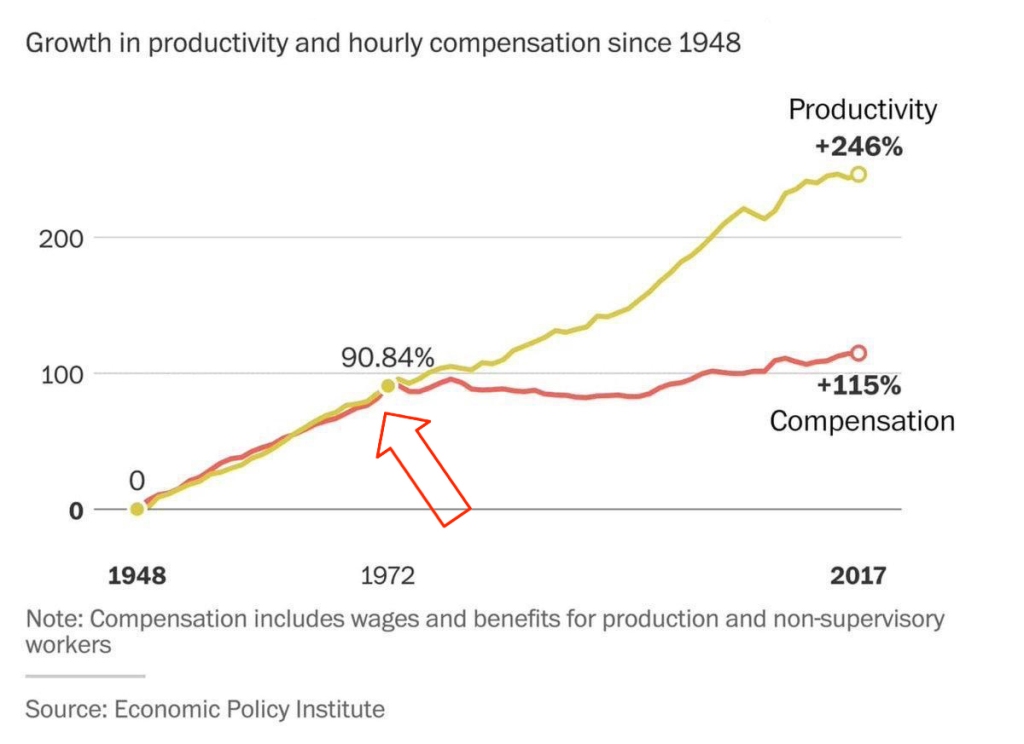 This chart shows that from 1948 to the early 1970s, productivity and wages grew together.\
But after the end of the gold standard in 1971 — the connection broke. Productivity kept rising, but real wages stalled.
This chart shows that from 1948 to the early 1970s, productivity and wages grew together.\
But after the end of the gold standard in 1971 — the connection broke. Productivity kept rising, but real wages stalled.👉 This means: you work more, better, faster — but buy less.
🔗 Source: wtfhappenedin1971.com
When you must spend today because tomorrow it’ll be worth less — that’s rewarding impulse and punishing long-term thinking.
Bitcoin offers a different environment:\ – Savings work\ – Long-term thinking is rewarded\ – The price of the future is calculated, not forced by a printing press
📌 Inflation can be a tool. But in government hands, it became a weapon — a slow, inevitable upward redistribution of wealth.
Indexing is weak compensation if bread is up 15% and your “increase” is only 5%.
\ \ Statement: War is not growth, but a reallocation of resources into destruction.
Criticism: war can spur technological leaps (Internet, GPS, nuclear energy — all from military programs). "Military Keynesianism" was a real model.
4. “War Drives R&D”
Yes, wars sometimes give rise to tech spin-offs: Internet, GPS, nuclear power — all originated from military programs.
But that doesn’t make war a source of progress — it makes tech a byproduct of catastrophe.
“War reallocates resources toward destruction — not growth.”
Progress doesn’t happen because of war — it happens despite it.
If scientific breakthroughs require a million dead and burnt cities — maybe you’ve built your economy wrong.
💬 Even Michael Saylor said:
“If you need war to develop technology — you’ve built civilization wrong.”
No innovation justifies diverting human labor, minds, and resources toward destruction.\ War is always the opposite of efficiency — more is wasted than created.
🧠 Bitcoin, on the other hand, is an example of how real R&D happens without violence.\ No taxes. No army. Just math, voluntary participation, and open-source code.
📌 Military Keynesianism is not a model of progress — it’s a symptom of a sick monetary system that needs destruction to reboot.
Bitcoin shows that coordination without violence is possible.\ This is R&D of a new kind: based not on destruction, but digital creation.
Statement: Bitcoin isn’t “Gold 1.0,” but an improved version: divisible, verifiable, unseizable.
Criticism: Bitcoin has no physical value; "unseizability" is a theory;\ Gold is material and autonomous.
5. “Bitcoin Has No Physical Value”
And gold does? Just because it shines?
Physical form is no guarantee of value.\ Real value lies in: scarcity, reliable transfer, verifiability, and non-confiscatability.
Gold is:\ – Hard to divide\ – Hard to verify\ – Expensive to store\ – Easy to seize
💡 Bitcoin is the first store of value in history that is fully free from physical limitations, and yet:\ – Absolutely scarce (21M, forever)\ – Instantly transferable over the Internet\ – Cryptographically verifiable\ – Controlled by no government
🔑 Bitcoin’s value lies in its liberation from the physical.\ It doesn’t need to be “backed” by gold or oil. It’s backed by energy, mathematics, and ongoing verification.
“Price is what you pay, value is what you get.” — Warren Buffett
When you buy bitcoin, you’re not paying for a “token” — you’re gaining access to a network of distributed financial energy.
⚡️ What are you really getting when you own bitcoin?\ – A key to a digital asset that can’t be faked\ – The ability to send “crystallized energy” anywhere on Earth\ – A role in a new accounting system that runs 24/7/365\ – Freedom: from banks, borders, inflation, and force
📉 Bitcoin doesn’t require physical value — because it creates value:\ Through trust, scarcity, and energy invested in mining.\ And unlike gold, it was never associated with slavery.
Statement: There’s no “income without risk” in Bitcoin: just hold — you preserve; want more — invest, risk, build.
Criticism: contradicts HODL logic; speculation remains dominant behavior.
6. “Speculation Dominates”
For now — yes. That’s normal for the early phase of a new technology. Awareness doesn’t come instantly.
What matters is not the motive of today’s buyer — but what they’re buying.
📉 A speculator may come and go — but the asset remains.\ And this asset is the only one in history that will never exist again. 21 million. Forever.
📌 Look deeper. Bitcoin has:\ – No CEO\ – No central issuer\ – No inflation\ – No “off switch”
💡 It’s not a stock. Not a startup. Not someone’s project.\ It’s a new foundation for trust.\ It’s opting out of a system where freedom is a privilege you’re granted under conditions.
🧠 People say: “Bitcoin can be copied.”\ Theoretically — yes.\ Practically — never.
Here’s what you’d need to recreate Bitcoin:\ – No pre-mine\ – A founder who disappears and never sells\ – No foundation or corporation\ – Tens of thousands of nodes worldwide\ – 701 million terahashes of hash power\ – Thousands of devs writing open protocols\ – Hundreds of global conferences\ – Millions of people defending digital sovereignty\ – All that without a single marketing budget
That’s all.
🔁 Everything else is an imitation, not a creation.\ Just like you can’t “reinvent fire” — Bitcoin can only exist once.
Statements:\ The Russia's '90s weren’t a free market — just anarchic chaos without rights protection.*\ Unlike fiat or even dollars, Bitcoin is the first asset with real defense — from governments, inflation, even thugs.\ And yes, even if your barber asks about Bitcoin — maybe it's not a bubble, but a sign that inflation has already hit everyone.
Criticism: Bitcoin’s protection isn’t universal — it works only with proper handling and isn’t available to all.\ Some just want to “get rich.”\ None of this matters because:
-
Bitcoin’s volatility (-30% in a week, +50% in a month) makes it unusable for price planning or contracts.
-
It can’t handle mass-scale usage.
-
To become currency, geopolitical will is needed — and without the first two, don’t even talk about the third.\ Also: “Bitcoin is too complicated for the average person.”
7. “It’s Too Complex for the Masses”
It’s complex — if you’re using L1 (Layer 1). But even grandmas use Telegram. In El Salvador, schoolkids buy lunch with Lightning. My barber installed Wallet of Satoshi in minutes right in front of me — and I now pay for my haircut via Lightning.
UX is just a matter of time. And it’s improving. Emerging tools:\ Cashu, Fedimint, Fedi, Wallet of Satoshi, Phoenix, Proton Wallet, Swiss Bitcoin Pay, Bolt Card / CoinCorner (NFC cards for Lightning payments).
This is like the internet in 1995:\ It started with modems — now it’s 4K streaming.
8. “Can’t Handle the Load”
A common myth.\ Yes, Bitcoin L1 processes about 7 transactions per second — intentionally. It’s not built to be Visa. It’s a financial protocol, just like TCP/IP is a network protocol. TCP/IP isn’t “fast” or “slow” — the experience depends on the infrastructure built on top: servers, routers, hardware. In the ’90s, it delivered text. Today, it streams Netflix. The protocol didn’t change — the stack did.
Same with Bitcoin: L1 defines rules, security, finality.\ Scaling and speed? That’s the second layer’s job.
To understand scale:
| Network | TPS (Transactions/sec) | | --- | --- | | Visa | up to 24,000 | | Mastercard | \~5,000 | | PayPal | \~193 | | Litecoin | \~56 | | Ethereum | \~20 | | Bitcoin | \~7 |
\ ⚡️ Enter Lightning Network — Bitcoin’s “fast lane.”\ It allows millions of transactions per second, instantly and nearly free.
And it’s not a sidechain.
❗️ Lightning is not a separate network.\ It uses real Bitcoin transactions (2-of-2 multisig). You can close the channel to L1 at any time. It’s not an alternative — it’s a native extension built into Bitcoin.\ Also evolving: Ark, Fedimint, eCash — new ways to scale and add privacy.
📉 So criticizing Bitcoin for “slowness” is like blaming TCP/IP because your old modem won’t stream YouTube.\ The protocol isn’t the problem — it’s the infrastructure.
🛡️ And by the way: Visa crashes more often than Bitcoin.
9. “We Need Geopolitical Will”
Not necessarily. All it takes is the will of the people — and leaders willing to act. El Salvador didn’t wait for G20 approval or IMF blessings. Since 2001, the country had used the US dollar as its official currency, abandoning its own colón. But that didn’t save it from inflation or dependency on foreign monetary policy. In 2021, El Salvador became the first country to recognize Bitcoin as legal tender. Since March 13, 2024, they’ve been purchasing 1 BTC daily, tracked through their public address:
🔗 Address\ 📅 First transaction
This policy became the foundation of their Strategic Bitcoin Reserve (SBR) — a state-led effort to accumulate Bitcoin as a national reserve asset for long-term stability and sovereignty.
Their example inspired others.
In March 2025, U.S. President Donald Trump signed an executive order creating the Strategic Bitcoin Reserve of the USA, to be funded through confiscated Bitcoin and digital assets.\ The idea: accumulate, don’t sell, and strategically expand the reserve — without extra burden on taxpayers.
Additionally, Senator Cynthia Lummis (Wyoming) proposed the BITCOIN Act, targeting the purchase of 1 million BTC over five years (\~5% of the total supply).\ The plan: fund it via revaluation of gold certificates and other budget-neutral strategies.
📚 More: Strategic Bitcoin Reserve — Wikipedia
👉 So no global consensus is required. No IMF greenlight.\ All it takes is conviction — and an understanding that the future of finance lies in decentralized, scarce assets like Bitcoin.
10. “-30% in a week, +50% in a month = not money”
True — Bitcoin is volatile. But that’s normal for new technologies and emerging money. It’s not a bug — it’s a price discovery phase. The world is still learning what this asset is.
📉 Volatility is the price of entry.\ 📈 But the reward is buying the future at a discount.
As Michael Saylor put it:
“A tourist sees Niagara Falls as chaos — roaring, foaming, spraying water.\ An engineer sees immense energy.\ It all depends on your mental model.”
Same with Bitcoin. Speculators see chaos. Investors see structural scarcity. Builders see a new financial foundation.
💡 Now consider gold:
👉 After the U.S. abandoned the gold standard in 1971, gold surged from \~$35 to over $800 in a decade — while suffering wild -40% to -60% crashes along the way.\ \ 📈 Gold Price Chart — Macrotrends\ \ Nobody said, “This can’t be money.” \ Because money is defined not by volatility, but by scarcity, adoption, and trust — which build over time.
📊 The more people save in Bitcoin, the more its volatility fades.
This is a journey — not a fixed state.
We don’t judge the internet by how it worked in 1994.\ So why expect Bitcoin to be the “perfect currency” in 2025?
It grows bottom-up — without regulators’ permission.\ And the longer it survives, the stronger it becomes.
Remember how many times it’s been declared dead.\ And how many times it came back — stronger.
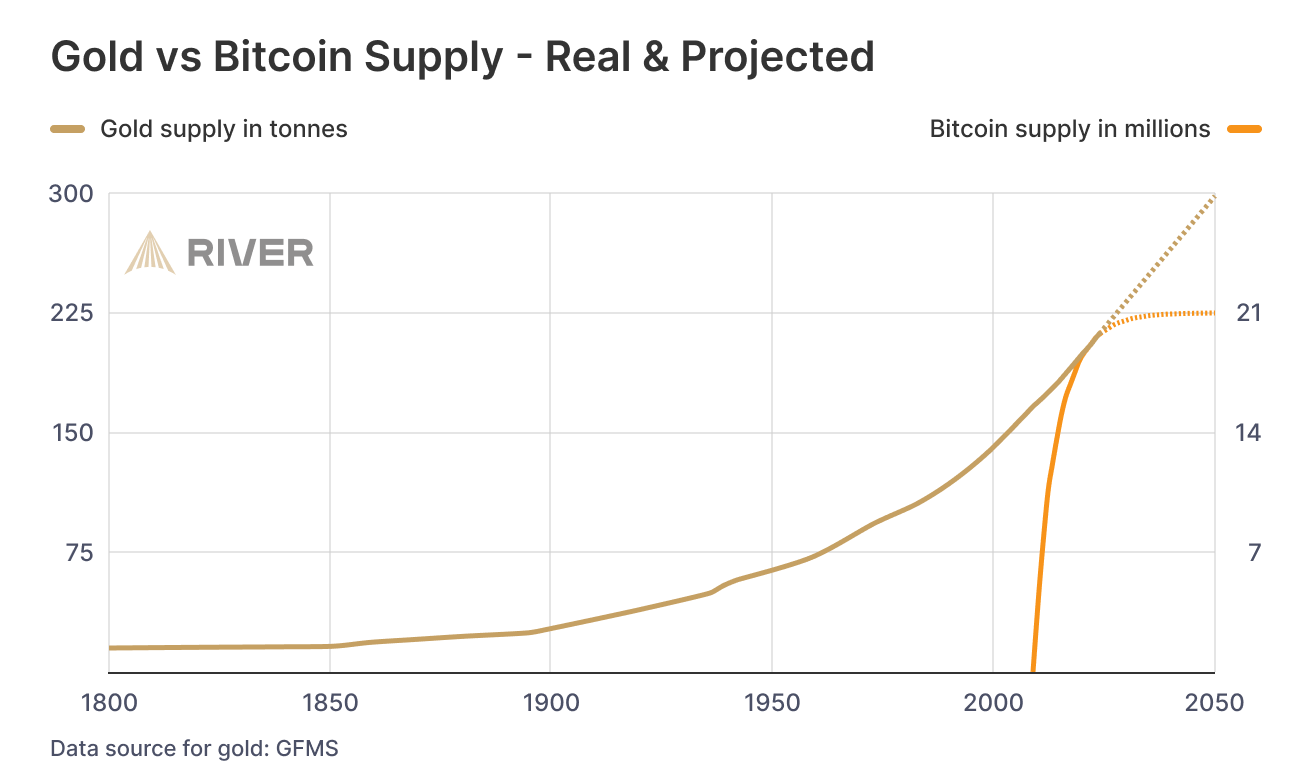
📊 Gold vs. Bitcoin: Supply Comparison
This chart shows the key difference between the two hard assets:
🔹 Gold — supply keeps growing.\ Mining may be limited, but it’s still inflationary.\ Each year, there’s more — with no known cap: new mines, asteroid mining, recycling.
🔸 Bitcoin — capped at 21 million.\ The emission schedule is public, mathematically predictable, and ends completely around 2140.
🧠 Bottom line:\ Gold is good.\ Bitcoin is better — for predictability and scarcity.
💡 As Saifedean Ammous said:
“Gold was the best monetary good… until Bitcoin.”
While we argue — fiat erodes every day.
No matter your view on Bitcoin, just show me one other asset that is simultaneously:
– immune to devaluation by decree\ – impossible to print more of\ – impossible to confiscate by a centralized order\ – impossible to counterfeit\ – and, most importantly — transferable across borders without asking permission from a bank, a state, or a passport
💸 Try sending $10,000 through PayPal from Iran to Paraguay, or Bangladesh to Saint Lucia.\ Good luck. PayPal doesn't even work there.
Now open a laptop, type 12 words — and you have access to your savings anywhere on Earth.
🌍 Bitcoin doesn't ask for permission.\ It works for everyone, everywhere, all the time.
📌 There has never been anything like this before.
Bitcoin is the first asset in history that combines:
– digital nature\ – predictable scarcity\ – absolute portability\ – and immunity from tyranny
💡 As Michael Saylor said:
“Bitcoin is the first money in human history not created by bankers or politicians — but by engineers.”
You can own it with no bank.\ No intermediary.\ No passport.\ No approval.
That’s why Bitcoin isn’t just “internet money” or “crypto” or “digital gold.”\ It may not be perfect — but it’s incorruptible.\ And it’s not going away.\ It’s already here.\ It is the foundation of a new financial reality.
🔒 This is not speculation. This is a peaceful financial revolution.\ 🪙 This is not a stock. It’s money — like the world has never seen.\ ⛓️ This is not a fad. It’s a freedom protocol.
And when even the barber starts asking about Bitcoin — it’s not a bubble.\ It’s a sign that the system is breaking.\ And people are looking for an exit.
For the first time — they have one.
💼 This is not about investing. It’s about the dignity of work.
Imagine a man who cleans toilets at an airport every day.
Not a “prestigious” job.\ But a crucial one.\ Without him — filth, bacteria, disease.
He shows up on time. He works with his hands.
And his money? It devalues. Every day.
He doesn’t work less — often he works more than those in suits.\ But he can afford less and less — because in this system, honest labor loses value each year.
Now imagine he’s paid in Bitcoin.
Not in some “volatile coin,” but in hard money — with a limited supply.\ Money that can’t be printed, reversed, or devalued by central banks.
💡 Then he could:
– Stop rushing to spend, knowing his labor won’t be worth less tomorrow\ – Save for a dream — without fear of inflation eating it away\ – Feel that his time and effort are respected — because they retain value
Bitcoin gives anyone — engineer or janitor — a way out of the game rigged against them.\ A chance to finally build a future where savings are real.
This is economic justice.\ This is digital dignity.
📉 In fiat, you have to spend — or your money melts.\ 📈 In Bitcoin, you choose when to spend — because it’s up to you.
🧠 In a deflationary economy, both saving and spending are healthy:
You don’t scramble to survive — you choose to create.
🎯 That’s true freedom.
When even someone cleaning floors can live without fear —\ and know that their time doesn’t vanish... it turns into value.
-
-
 @ cefb08d1:f419beff
2025-05-19 11:38:06
@ cefb08d1:f419beff
2025-05-19 11:38:06Source : https://mymodernmet.com/2024-dog-photography-awards/
https://stacker.news/items/983647
-
 @ cefb08d1:f419beff
2025-05-19 07:13:51
@ cefb08d1:f419beff
2025-05-19 07:13:51https://stacker.news/items/983539
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-19 00:31:55
@ 5d4b6c8d:8a1c1ee3
2025-05-19 00:31:55We have our conference finalists: - Indiana (4) @ New York (3) - Minnesota (6) @ OKC (1)
Pick one team to advance to the finals and one player to win Conference Finals MVP. One player from each matchup will be named MVP.
The scoring this round is 4 points + seed value for picking a winner and 4 points for picking an MVP. The maximum points this round are 14.
Current Scores | Stacker | Points | |----------|-------| | @Undisciplined | 35 | | @grayruby | 32 | | @gnilma | 28 | | @fishious | 21 | | @WeAreAllSatoshi | 20 | | @BlokchainB | 19 | | @Coinsreporter | 19 | | @Carresan | 18 | | @Car | 9 |
SGA was the leading scorer of round 2
https://stacker.news/items/983402
-
 @ 8d34bd24:414be32b
2025-05-18 20:43:56
@ 8d34bd24:414be32b
2025-05-18 20:43:56We are all supposed to share Jesus and His word with those around us. We are called to:
but sanctify Christ as Lord in your hearts, always being ready to make a defense to everyone who asks you to give an account for the hope that is in you, yet with gentleness and reverence (1 Peter 3:15)
We should daily pray to God, read the Bible, and share Jesus with others. Some Christians will choose to go into full-time service to God. They will be pastors or missionaries. They will work for churches, Christian schools, and other Christian ministries. Of course, not everyone will make serving Jesus a career. That doesn’t mean the non-career Christians have no job to do. We are all to be a light to this world.
There is one ministry, though, that I’d argue is most important: sharing the gospel with and discipling our children.
These words, which I am commanding you today, shall be on your heart. You shall teach them diligently to your sons and shall talk of them when you sit in your house and when you walk by the way and when you lie down and when you rise up. (Deuteronomy 6:6-7)
This passage may have been written in the Old Testament, but I’d argue that it is even more true now that we have the truth of Jesus Christ, “the way, the truth, and the life.” If the Jews were called to diligently teach their kids the law, how much more should Christians diligently teach their kids the wonderous works and words of Jesus?
Train up a child in the way he should go, Even when he is old he will not depart from it. (Proverbs 22:6)
We should be so excited about what Jesus has done for us that it flows out of us in our daily lives. We should have a strong desire to learn God’s word and to share it with others, especially our children. We should share our excitement about Jesus with our kids. We should share our gratefulness for all Jesus has done for us. We should share our excitement about doing God’s work. Our children should see our faith in all we do and say.
Taking our kids to church Sunday morning and to Sunday school or youth group once a week is not going to teach our kids the importance of faith in Jesus. Praying openly at meals, at bedtime, when we hear about someone in need, and when a difficult situation happens teaches our kids to rely on Jesus. Reading our Bibles in front of our kids and doing daily devotions (at whatever time works for you, but we do evenings) teaches them the importance of the Scriptures. Acting according to a Biblical worldview and taking the time to explain to our kids the answers to the hard questions when the culture contradicts the Bible. This may mean taking the time to research answers to your kids’ questions because you don’t know the answer. Being patient with our kids, and even apologizing to them when we fail, teaches them to be humble and to repent. As the old saying goes, “morals are caught more than taught.” Also faith in Jesus is caught more than taught.
We need to live Godly lives that are different than the culture, remembering that our children are always watching, even when they are quite young and can’t articulate what they are learning.
We need to actively teach God’s word. This may be summarizing principles when they are young, but as soon as possible, this should include reading God’s word to our kids. (My daily reading is usually in an NASB Bible, but it is difficult for a young child to understand with its long, complex sentences, so I recommend something like the NLT Bible for children.)
“Now this is the commandment, the statutes and the judgments which the Lord your God has commanded me to teach you, that you might do them in the land where you are going over to possess it, so that you and your son and your grandson might fear the Lord your God, to keep all His statutes and His commandments which I command you, all the days of your life, and that your days may be prolonged. (Deuteronomy 6:1-2) {emphasis mine}
We want to share all of our knowledge of God and the Bible with our kids, grandkids, and great grandkids. We want to disciple our kids into strong faith in God and knowledge of the Bible, so they are capable of training their kids and their grandkids. We want to multiply faith in our families.
It is definitely good to have scheduled, intentional times of training our kids about the Bible. This could be part of homeschooling (which I strongly recommend). This could be family devotions, but we want teaching our kids about God to be just a natural part of life.
You shall teach them to your sons, talking of them when you sit in your house and when you walk along the road and when you lie down and when you rise up. (Deuteronomy 11:19)
Talking about what God has done in our lives, what we have learned about in our personal Bible study, and how the Bible relates to things we see in life should all naturally flow out of our interactions together. Talk about what the Bible says about a subject you hear on the news. Talk about what the Bible says about what is happening in a movie you watch. Talk about what the Bible says about the decisions you and your kids are having to make. Talk about what the Bible says about your kids’ relationship with each other and their friends and parents. God should be a normal part of everything in life.
We also want to make sure our actions don’t drive our kids away from God.
Fathers, do not provoke your children to anger, but bring them up in the discipline and instruction of the Lord. (Ephesians 6:4)
The Bible does not make light of our need to train our kids in faith.
Discipline your son while there is hope, And do not desire his death. (Proverbs 19:18)
This is so important that failure to train up our kids in faith is considered desiring our kid’s death.
God finds this training so critical, He also addresses it from the kid’s point of view and commands them to listen to their parent’s teaching.
My son, give attention to my words;\ Incline your ear to my sayings.\ Do not let them depart from your sight;\ Keep them in the midst of your heart.\ For they are life to those who find them\ And health to all their body.\ Watch over your heart with all diligence,\ For from it flow the springs of life. (Proverbs 4:20-23)
In Proverbs 31, the Bible gives the best explanation of a Godly woman and mother.
She opens her mouth in wisdom,\ And the teaching of kindness is on her tongue.\ She looks well to the ways of her household,\ And does not eat the bread of idleness.\ *Her children rise up and bless her*;\ Her husband also, and he praises her, saying:\ “Many daughters have done nobly,\ But you excel them all.” (Proverbs 31:26-29)
A Mom should continually “open her mouth in wisdom,” and teach kindly. A mother who fulfills this commandment faithfully is promised that “Her children rise up and bless her.” Being loved and appreciated by our kids is a wonderful blessing, but even greater is knowing that we will see our children with us in heaven.
May God guide you and encourage you as you teach, train, and discipline your kids to know their God, Creator, and Savior.
Trust Jesus.
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-18 16:24:01
@ 5d4b6c8d:8a1c1ee3
2025-05-18 16:24:01First, the caveat: Yes, I understand that there's a consistent libertarian case for free trade as a policy position.
With all the discourse around tariffs, I wanted to highlight something of a moral oddity in the arguments being used by many free trade libertarians (I am a free trade libertarian, btw): namely, the idea that we (Americans) should happily take advantage of subsidized exports from poorer countries.
I do agree with the economics of the argument: By subsidizing exports, other countries are imposing a deadweight loss on themselves and passing savings along to US consumers.
Why are libertarians celebrating this, though? Poor, oppressed foreigners are being stolen from by their authoritarian governments and American consumers are benefiting from it financially. Thinking this is a good situation is odd and thinking you have a right to take part in it is even stranger.
Libertarians certainly understand that subsidies are wrong and economically harmful, and that they benefit a select group of politically connected cronies. Nothing about that changes just because it's happening in a foreign country and your grocery bill benefits from it.
Saying "That's how they run their country. It's none of our business." is a plea to moral relativism, which libertarians generally avoid. Libertarians also usually understand that the "they" who rule is not the same as the "they" who are ruled. Is it just too uncomfortable to acknowledge being the beneficiary of abuse?
I can't help but draw parallels to the abolitionists of two hundred years ago, who refused to buy the products of slaves. I think they're mostly viewed as having been "on the right side of history", but they're probably on the "wrong" side of most "free trade" arguments. Another of those arguments being that it doesn't help the poor oppressed foreigner to stop doing business with their oppressor (yes, many lefties get all mixed up about who the oppressors are).
Anyway, I have no brilliant conclusion to offer. What do you all think?
https://stacker.news/items/983054
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-18 14:42:48
@ 5d4b6c8d:8a1c1ee3
2025-05-18 14:42:48What do we mean when we talk about "fitness"? The word implies a connection to a higher purpose: "Fitness for what?"
Biologically, "fitness" refers to the propensity of an organism to pass on it's genes. Biological fitness is clearly context dependent: i.e. an anaconda isn't so fit if it gets moved to the arctic. I think we can build on that, while making it more human.
I think of fitness as our capacity to thrive in our environment. That's going to be different for each of us, depending on our environment and our preferences. However, there are some useful implications of thinking of fitness this way: 1. Chores, errands, work, play, and family activities might be the best kind of exercise, since they are physical activities that are directly tied to your lifestyle. 2. Supplemental exercise should be geared towards your lifestyle and improving your ability to accomplish things you need to be able to do. 3. There's no such thing as a universal "best exercise" or "best diet", because we all have different fitness objectives. 4. "Fitness" is not static: We do different things and have different priorities at different points in our lives, so our fitness goals should change over time. Many of us will even have seasonal fitness changes, since we don't do the same things in winter as we do in summer.
How do you all think about "fitness"?
Is it a highfalutin ivory tower concept or is it just ABs?
https://stacker.news/items/982981
-
 @ 7460b7fd:4fc4e74b
2025-05-18 11:02:09
@ 7460b7fd:4fc4e74b
2025-05-18 11:02:09比特币持有者在 iPhone 上的安全使用注意事项
引言:iPhone 与安卓的对比
当涉及移动设备安全,比特币持有者面临着在 iPhone 和安卓设备之间的选择。从安全硬件来看,安卓阵营中确有一些型号配备了类似于 Apple Secure Enclave 的硬件安全模块,例如 Google Pixel 手机内置的 Titan M/M2 安全芯片,用于保障启动流程和存储敏感数据us.norton.com;三星的旗舰机型则集成了 Samsung Knox 多层安全平台,经过多国政府机构认证,可在硬件层面保护设备及其中数据us.norton.com。这些安全措施大大提升了设备抵御恶意攻击和数据泄露的能力。然而,需要注意的是:具备此类高级安全特性的安卓机型在市场上相对少见,并非安卓阵营的普遍标准us.norton.com。安卓生态高度碎片化,不同厂商的安全实践差异悬殊;除了少数注重安全的厂商(如 Google、Samsung)外,许多设备缺乏统一的安全保障水平us.norton.com。尤其在二手市场上,安卓设备型号繁杂且来源不一,一些旧款或改装机型可能缺少最新的安全芯片或更新,使安全性难以得到保证。
相比之下,Apple iPhone 全系列自带硬件级的安全隔区(Secure Enclave),统一的闭源系统和严格的应用审核使其安全措施在所有设备上保持一致us.norton.com。同时,iPhone 引入的 Face ID(三维结构光人脸识别)在生物识别安全性上具有独特优势。Apple官方数据显示,Face ID 被他人解锁的概率只有 百万分之一,远低于指纹识别的五万分之一。这源于Face ID利用红外点阵投射捕捉面部3D结构,难以被照片或面具所破解,大幅减少了伪造生物特征解锁的风险。此外,相较许多安卓手机仍依赖的二维人脸识别或电容/光学指纹,Face ID 在抗攻击能力上更胜一筹——例如普通指纹残留可能被提取复制,而二维人脸解锁曾被照片轻易骗过,但Face ID的深度感应技术有效避免了这些漏洞。
综上所述,在移动设备安全领域,iPhone 为比特币等高价值敏感资产的持有者提供了更为稳健和统一的安全基础。尽管某些高端安卓手机具有可圈可点的安全功能,但鉴于这类机型凤毛麟角、安卓设备更新和管控的不统一,以及生物识别方案的差异,我们强烈建议将 iPhone 作为比特币手持设备的唯一选择。从硬件加密到生物识别,iPhone 的封闭生态和领先技术能为数字资产提供更可靠的防护,而安卓设备在这一场景下则存在诸多先天不足。
小结: 安卓阵营虽有Pixel Titan芯片、Samsung Knox等亮点,但安全机型数量有限且良莠不齐;iPhone凭借统一的安全架构和先进的Face ID,在保护敏感数据方面更胜一筹。为确保比特币等资产安全,选择安全可靠的iPhone 是明智之举。
iPhone 安全配置指南
选择了 iPhone 作为比特币存取和通讯设备后,仍需进行细致的安全设置,以最大化利用其安全潜力。以下是针对比特币持有者的 iPhone 安全配置要点:
-
禁用 Face ID/Touch ID 生物解锁,改用强PIN码: 建议关闭面容ID解锁功能,改用6位以上的数字PIN码(或更复杂的字母数字密码)作为解锁方式。在紧急情况下,生物识别容易被他人强制利用(例如他人将手机对准机主面部强行解锁),而记忆型的PIN码只有持有人知晓,更难以被胁迫获取。此外,法律上某些地区对强制提供生物特征和提供密码有所区别,这也使得使用PIN码在极端情况下更有保障。
-
启用自动锁定(1分钟) 将设备设为闲置1分钟后自动锁定屏幕。从安全角度出发,锁定等待时间越短越好。1分钟的设置可确保即使暂时离开或疏忽,设备也会很快上锁,防范他人乘虚而入。养成随手锁屏的习惯固然重要,但有了短自动锁定时间作为双重保障,安全性更上一层楼。
-
开启输错10次自动抹除: 在“设置 > 面容ID/触控ID与密码”中启用“连续输错10次密码抹掉数据”功能。一旦有人反复尝试猜测密码,该功能会在第十次错误尝试后自动抹除手机数据。很多用户担心该设置存在风险,但事实上 误触发的可能性极低。sspai.comsspai.com实际测试表明,iPhone在多次输错密码时会触发累进的延迟惩罚机制:第五次错误需要等待1分钟,第六次错误等待5分钟,第7-8次各等待15分钟,第9次等待1小时sspai.comsspai.com。要连续进行十次独立的错误尝试至少需要约96分钟,在现实中“熊孩子”乱按连续清空数据几乎不可能发生sspai.com。相反,该功能对抗暴力破解极为有效——正如2015年圣贝纳迪诺恐怖袭击案中,嫌犯所用的iPhone就启用了十次错误清除,使FBI也无法轻易尝试破解en.wikipedia.org。总之,此项设置能将设备落入他人之手时的数据泄露风险降至最低。
-
利用应用级 Face ID 控制(iOS 18+):升级至iOS 18或更新版本,充分利用其新增的应用锁定功能。长按主屏某个应用图标,可以找到“需要Face ID”选项,将该应用加锁theverge.com。被加锁的应用每次打开都需要通过Face ID身份验证(即使手机已解锁)。建议对 聊天通讯、密码管理、交易所App 等敏感应用启用此功能。例如,将微信、Signal、邮件客户端等设置为打开需Face ID验证,以防范他人在您手机解锁的短暂间隙内获取其中内容。应用级Face ID锁定为设备提供了第二道防线:即使手机本身已解锁,敏感应用和数据仍受到保护。
-
建议购买第二台 iPhone 或 iPad 作为“备用解锁入口”: 利用 Apple 的“信任链”机制,为同一 Apple ID 配置多台受信任设备(如两台 iPhone 或 iPhone+iPad)。这样即使主设备丢失或被抹除,备用设备依然可以访问并恢复 iCloud 端到端加密数据。其安全本质类似于“1-of-N 多签”,即任一设备均可独立解锁所有云数据,但无需多设备联合协商,恢复更灵活。注意:这与比特币的m-of-n多签不同,Apple的信任链是单设备多入口,安全性和便利性权衡需根据个人需求评估。官方说明参见:Apple平台安全白皮书(Keychain与信任链)
-
建议购买 YubiKey 等硬件安全密钥作为 Apple ID 验证要素: 由于信任链机制下新设备加入时,身份验证成为潜在攻击点(如钓鱼、社工、短信劫持),推荐为 Apple ID 配置 YubiKey 或兼容 FIDO2/U2F 的硬件安全密钥。启用后,只有插入并触发硬件密钥的情况下,才能完成新设备授权、敏感操作或账户恢复,有效阻止网络钓鱼和大部分远程攻击。该方法可显著提升账户安全,降低因凭证泄漏或验证被劫持导致的信任链攻破风险。Apple 官方说明:为 Apple ID 添加安全密钥
通过上述配置,iPhone 将处于一个平衡了便利性和安全性的状态:日常解锁采用PIN码确保意外情况下设备不被强制解锁,短自动锁和十次清除严防暴力破解,而应用级加锁进一步保障重要数据不外泄。
小结: 按照以上指南对iPhone进行安全配置,可以大幅提升设备在实际使用中的抗攻击能力。生物识别解锁的取舍、自动锁定和清除机制、以及iOS 18引入的应用加锁功能相结合,全方位地巩固了手机作为比特币手持设备的安全基石。
关于自动抹除的常见质疑回应
启用“输错10次自动抹除”功能后,不少用户会提出疑虑,主要集中在两个方面:其一,担心儿童误操作或本人一时疏忽导致设备数据被抹掉;其二,担心万一手机数据被抹除,设备本身价值受损。针对这些质疑,我们进行如下回应:
-
“熊孩子乱按怎么办?” 前文已提及,iPhone设计了渐进延时机制,使得连续十次错误输入并非易事sspai.comsspai.com。孩子无意识地反复点击相同数字,系统只视为一次错误sspai.com;而多次不同错误则会触发越来越长的锁定时间,很难真的连续试满十次sspai.com。实践中,要触发十次错误清除需要近两个小时且每次输入都不同,这种情景极不现实sspai.com。因此,只要平时看护好设备,误抹除几乎无需担心。相反,如果没有该功能,一旦设备遗失或被不法分子获取,后果将不堪设想——对方可以在足够时间和专业工具协助下尝试无限次解锁,从而获取您手机中的一切秘密。
-
“数据没了岂不可惜?” 我们强调,比特币持有者手机中存储的敏感信息价值远超设备本身。手机里可能有助记词、私钥线索、交易记录截图,甚至包含您社交账户中关于资产的对话。在攻击者眼中,这些数据的价值胜过一部手机。与其担心设备被误清除,不如担心设备落入他人之手数据遭泄露的风险。况且,对于重要数据您应当早有备份(下文将讨论启用iCloud云备份的问题)。即使真发生误清除,有备份在手也能恢复;但若数据被不法分子窃取,一旦造成资产损失将无法挽回。因此,从风险权衡来看,“宁可误删,不可被盗”——自动抹除是最后一道保障,在极端情况下保护您的数字资产不被侵害。
总而言之,这一功能的利远大于弊。儿童误触可以通过良好监护和系统延时设计来防范,而一旦启用,您将获得巨大的安心:手机若遭试图破解,可以自毁以保全数据安全。这正是比特币持有者应有的安全理念:舍弃设备保安全,数据和资产永远优先于硬件。随着良好备份策略的配合(例如iCloud加密备份),启用自动抹除几乎没有后顾之忧。
小结: 针对自动抹除功能的疑虑更多是误解。iPhone的机制使得误触发几率极低,而其提供的数据安全保障却是无可替代的。比特币等敏感资产持有者应放下顾虑,优先保护数据安全——哪怕代价是设备被清除,也胜过数据落入他人之手。
iCloud 备份的争议与建议
在确保本地设备安全的同时,妥善备份数据同样关键。对于比特币持有者而言,启用 iCloud 云备份可以提供额外的一层安心:万一设备遗失、损坏或被抹除后,仍有机会恢复重要信息。然而,围绕iCloud备份的安全性一直存在争议,我们在此详细分析并给出建议:
首先强烈建议在启用iCloud备份的同时,务必开启「高级数据保护」(Advanced Data Protection, ADP)。默认情况下,iCloud云备份的数据加密密钥由Apple掌管,这意味着苹果公司在法律要求下能够解密并提供您的备份数据support.apple.comsupport.apple.com。而开启高级数据保护后,备份所涉及的大部分数据将采用端对端加密,只有您的受信任设备掌握解锁密钥support.apple.com。据苹果官方说明,在ADP模式下,即便苹果公司也无法读取您的备份内容support.apple.com。因此,高级数据保护能够将使用云备份可能带来的隐私泄露风险降至最低(前提是您妥善保管好自己的账户和恢复密钥)。
启用云备份常见的疑虑是:“会不会把我的钱包私钥也备份上去,万一云被攻破岂不危险?” 实际上,多数主流比特币/加密钱包软件不会将核心密钥(如助记词或扩展公钥xpub)存储在云备份中。很多钱包在设计时就要求用户自行备份助记词,而不会把这些高度敏感的数据写入应用沙盒,可被iCloud备份抓取。同样地,一些钱包应用甚至提醒用户关闭iCloud备份以防助记词泄露support.wallet.coinex.com。换言之,开启iCloud备份并不会将您的私钥上传(除非个别钱包特别设置了云同步,但大多数非托管钱包都没有这么做)。当然,为审慎起见,您可以查阅所用钱包的文档或设置,确认其是否有备份敏感信息到云的选项,并据此做出取舍。
与此同时,我们更加关心的是其他应用的数据完整备份。对于比特币持有者来说,聊天记录、笔记文档和工作应用的数据往往同样敏感且重要。例如,常用通讯软件(微信、Telegram、Signal 等)中的聊天可能涉及交易细节或人脉网络;办公应用如钉钉、飞书则包含财务往来或业务资料。这些应用的数据都会包含在iCloud整机备份中并被完整保存,一旦手机丢失或损坏,可以通过云备份原样恢复。support.apple.com值得一提的是,在高级数据保护开启且不泄漏密钥的前提下,这些备份数据即使存储在苹果服务器上也是安全的,第三方无法解读其中内容。
进一步的好处是:利用备份进行调查取证。假设最坏情况发生——您的手机被抹除或遗失,但是事先有一份最新的iCloud备份。在紧急需要时,您可以在一台新的iPhone上恢复这份备份。在恢复完成后,切断新设备的网络连接(拔掉SIM卡或不连Wi-Fi)。由于备份恢复会还原您的应用登录状态和本地数据,新设备在离线情况下将维持原手机当时的登录环境。您可以打开聊天应用、邮件、照片等查看内容,就像原手机一样。离线操作确保应用不会因为检测到新设备而要求重新登录,也避免了云端数据被远程清除的可能。这对于事后取证、提供线索给执法部门或自我调查都极为有利。比如,若涉及盗窃诈骗案件,这部离线恢复的手机里保留的聊天记录、交易凭证可以作为关键证据。而一旦联网,这些应用可能出于安全考虑登出账户或拉取最新状态,反而不利于保留原始证据。因此,有意识地保存一份完整云备份,并在需要时以离线方式恢复,是一种非常巧妙的应对策略。
小结: 尽管人们对云备份心存疑虑,但通过启用高级数据保护,iCloud备份既能提供数据恢复便利,又充分保障了隐私安全。大多数加密钱包不会上传私钥等核心数据,而聊天、办公等应用的数据则可完整份以备不时之需。在平衡安全与可用性的前提下,开启iCloud备份(搭配ADP加密)是明智之举——它让您在设备意外损坏或丢失时依然有据可查、有据可证。
高级数据保护与密码学机制分析
最后,我们从更宏观的视角,结合真实案例和技术原理,深入探讨苹果设备与云服务的安全性,以及高级数据保护(ADP)所依赖的密码学机制。这部分将涵盖苹果在多个国家遭遇的解锁争议、ADP 的运作及其与实体安全密钥的配合、以及关于苹果是否存在解密后门的分析。
苹果与执法部门的解锁事件
过去数年间,多起高调事件凸显了设备加密与执法取证之间的矛盾。美国国会山骚乱事件(2021年1月6日)中,执法部门缴获了大量嫌疑人的手机。据报道,不少嫌犯使用的是iPhone,调查人员能够从苹果获取其中的数据 但途径主要是通过 iCloud 云备份 而非直接破解设备thedailybeast.com。由于当时高级数据保护尚未推出或未启用,苹果依然持有那些嫌疑人iCloud账户的备份密钥,因此在收到合法的执法请求后,苹果向FBI提供了嫌疑人的iCloud备份内容,其中包括视频、照片和聊天记录等关键证据thedailybeast.com。这些数据帮助当局重构了案件过程,也反映出如果用户没有使用端到端加密备份,云端数据在法律压力下并非牢不可破。
相反,在更早的**圣贝纳迪诺恐怖袭击案(2015)**中,FBI面对一部启用了强加密的嫌犯iPhone却陷入僵局。那是一个运行iOS 9的 iPhone 5C,开启了PIN码锁和10次输错清除功能en.wikipedia.org。由于该设备上的本地数据经过设备加密且苹果并不持有密钥,FBI无法提取其中信息,遂求助苹果公司要求破解。但苹果以维护所有用户安全为由拒绝编写后门固件来绕过安全限制,引发了一场著名的法律拉锯en.wikipedia.orgen.wikipedia.org。最终执法部门辗转通过第三方工具解锁了手机,但苹果的立场十分明确:即便面对恐怖主义案件,也不会为单次事件在系统中留下后门。这一事件凸显出现代iPhone设备本地加密之强大——在没有用户密码的情况下,即使连厂商都无能为力,除非另辟蹊径寻求系统或硬件漏洞。
iCloud 在中国与英国的访问争议
在不同国家,苹果围绕用户数据加密与政府监管的博弈也在上演。中国方面,自2018年以来苹果将中国大陆 iCloud 服务交由“云上贵州”公司运营,数据存储和加密密钥均留在境内zh.amnesty.org。依据中国《网络安全法》,云服务运营者有义务为执法和国家安全机关提供“技术支持和协助”zh.amnesty.org。这意味着若中国警方出于刑侦需要向云上贵州调取某用户的 iCloud 数据,该公司必须配合提供,几乎没有拒绝的空间zh.amnesty.org。更重要的是,苹果把中国用户的 iCloud 加密密钥也存放在中国,一旦收到合法命令要求解密数据,苹果和云上贵州只能遵从zh.amnesty.org。换言之,在标准数据保护模式下,中国当局有途径通过法律手段获取本地存储的iCloud明文数据。这引发了人们对隐私的担忧:如果没有端到端加密,中国的用户数据可能在政府要求下被查看。然而如果用户开启高级数据保护,使得苹果也无法解读备份内容,那么即便在中国,此举从技术上为用户争取到了更高的私密性(前提是中国地区允许开启ADP——截至目前,苹果并未在中国禁用该功能,国区用户依然可以自行启用高级数据保护support.apple.comsupport.apple.com)。
再看英国的情况。英国政府近年以打击犯罪和恐怖主义为由,不断向科技公司施压要求提供加密数据的后门访问权。2023年底,英国援引《调查权力法》(IPA)秘密向苹果发出“技术能力通知”(TCN),要求苹果在全球范围内为英国安全部门提供对加密iCloud内容的解锁途径cnbeta.com.tw。这实际上等同于要求苹果破坏其端到端加密体系,留出一个只有政府能用的后门。苹果对此断然拒绝,并做出强硬回应:宁愿撤除在英服务,也不会妥协安全底线cnbeta.com.tw。结果是,苹果选择在英国境内停止提供高级数据保护功能给新用户。已有启用ADP的英国用户被通知需在宽限期内手动将其关闭,否则将无法继续使用iCloud备份cnbeta.com.tw。苹果在声明中表示对此深感失望,但为了遵守当地法律别无他法cnbeta.com.tw。下面这张截图显示了英国用户在系统中看到的提示信息,明确告知ADP服务不再可用

苹果针对英国地区做出的ADP功能调整通知。英国政府要求能够解密用户数据,迫使苹果撤回了对英国用户的新端到端加密备份支持cnbeta.com.twcnbeta.com.tw。苹果声明强调只有用户本人才能解读其加密数据,并重申不会在产品中留下执法后门cnbeta.com.tw。
这一英国内外的罕见举措表明,各国政府正日益重视加密带来的执法障碍,而苹果则在平衡用户隐私和法律要求之间走钢丝。尽管英国的情况迫使苹果让步(取消当地ADP),但苹果并未真的为政府打造解密后门,而是通过限制功能来表明态度——这与其长期立场一致:绝不在加密产品中留后门,即使承受业务上的损失cnbeta.com.tw。
高级数据保护与安全密钥
高级数据保护(ADP) 是苹果于 iOS 16.2 引入的一项可选功能,其核心是在用户选择开启后,将包括设备备份在内的大部分 iCloud 数据升级为端到端加密存储support.apple.comsupport.apple.com。开启ADP有两个前提:账户已启用双重认证,以及设置了账户恢复联系人或恢复密钥,以防用户遗失访问权限support.apple.comsupport.apple.com。在ADP模式下,Apple不再持有绝大部分云数据的解锁密钥,这些密钥只存在于用户的受信任设备中support.apple.com。这意味着,即便苹果公司收到政府索取数据的要求或其服务器遭黑客攻击,没有密钥的加密数据对任何第三方都是无意义的乱码。正如苹果声明所言:“只有拥有数据的用户才能解密,Apple 无法访问端对端加密的数据”cnbeta.com.tw。可以说,ADP将用户云数据的主导权完全交还给用户自己,从而彻底消除了苹果方面潜在的数据泄露点。
为了进一步增强账户安全,苹果在_iOS 16.3_开始支持绑定实体安全密钥(如 YubiKey)作为 Apple ID 的额外两步验证方式sspai.com。过去Apple ID登录主要依赖密码+发送到受信设备的验证码,但假如用户Apple ID密码泄露,攻击者可能利用社会工程获取验证码。而引入实体安全密钥后,用户可以要求任何新的登录尝试都必须提供物理密钥认证才能完成。这相当于给 Apple ID 上了一把“硬件锁”。对于比特币持有者而言,这一步非常值得配置:即使黑客骗取了您的苹果账号密码,没有您的YubiKey或同类FIDO2安全密钥,他仍无法登录您的iCloud或停用您的ADP。安全密钥本身具有防钓鱼特性,它不会把可被重用的机密泄露给假网站,再加上密钥私藏于硬件内部不可导出,使得账户保护达到新的高度sspai.comsspai.com。简而言之,**“ADP + 硬件安全密钥”**的组合为用户云数据打造了双重护城河:前者确保云上数据加密不被窥探,后者确保账户本身不被劫持利用。
需要注意的是,启用ADP后如果遗失所有设备且忘记密码,苹果无法帮您找回数据support.apple.com。这就像您把保险箱钥匙只握在自己手里而不交给任何人保管,其安全性空前提高,但也意味着责任完全在您。因此请务必牢记Apple ID密码,保管好恢复密钥或紧急联系人。一旦平衡好便利与安全,这套机制将为您的数字资产提供堪比硬件钱包的云端保障。
后门密钥与私钥不可拆分性
现代加密体系的设计使得用户私钥与设备环境密不可分。在苹果的生态中,每台设备都拥有由硬件生成的唯一加密根密钥。例如,安全隔区(Secure Enclave)内嵌入了设备唯一标识符UID作为根密钥,UID由安全硬件随机生成并烧录至芯片中help.apple.com。这个UID既不与任何其他设备标识相关,也无法被设备外的任何人(包括苹果官方)获取help.apple.com。同时,用户的解锁密码与该UID进行数学“交织”(entangle),共同派生出加密密钥help.apple.com。换言之,设备硬件密钥和用户密码共同决定了数据加密密钥,没有这两者就无法还原密钥。这体现了用户私钥对设备及用户身份的强绑定——苹果没有第三方密钥可以绕过这一绑定关系help.apple.comhelp.apple.com。
从密码学角度来看,如果苹果试图在上述体系中插入一个额外的“后门密钥”,将面临巨大的技术困难,并且这样的异常极易被察觉。设想苹果通过异或(XOR)或 Shamir 密钥共享等方式,将一个后门密钥与用户密钥组合:
- 实现层面的异常:用户设备在正常情况下应当能够独立完成解密/签名操作。如果加入隐藏密钥份额,意味着设备单凭用户自己的密钥无法完成某些解密,必须依赖苹果持有的那一份。这样的改动会造成额外的密钥协商步骤或异常的解密失败。例如,若苹果将后门密钥与用户密钥异或生成实际工作密钥,那么单用用户密钥将无法解密出正确结果,设备可能需要静默地向苹果服务器请求密钥片段或进行额外计算。这类非预期的通信或计算步骤很容易被安全研究者通过流量分析或逆向工程发现端倪。再比如采用 Shamir’s Secret Sharing 等门限方案,如果苹果持有一份密钥碎片,设备在解密时就需要满足门限条件,这通常意味着需要苹果的参与或预置公钥,从而在协议日志中留下异常痕迹。任何偏离常规协议的做法——无论是多传输一段数据,还是多保存一段密钥信息——都可能成为研究者捕捉的线索。历史经验表明,密码协议中的“奇怪之处”往往预示潜在漏洞或后门:例如 NSA 推出的 Dual_EC_DRBG 伪随机数生成器由于使用了异常常数,被专家迅速怀疑存在后门;著名密码学家施奈尔(Bruce Schneier)就曾直言 Dual_EC_DRBG 中的后门“相当明显”,呼吁业界停止使用en.wikipedia.org。由此可见,试图暗中插入额外密钥会在数学实现上留下破绽,而资深密码学者和安全社区有足够能力识别这些反常之处。
进一步,从门限签名理论对比苹果现有密钥管理,可以加深这一不可行性的理解。门限密码学允许将密钥拆分给多方持有,只有达到预定门槛的份额才能重构密钥或执行签名解密toc.csail.mit.edumedium.com。其优点在于提高了密钥托管的安全性,需要多方协作才能解锁秘密。然而,这种机制是公开设计的一部分,各参与方和流程都是明示的。例如在某些区块链多重签名方案中,多个私钥持有者共同生成交易签名,每个人都知晓门限机制的存在。相较之下,苹果在产品中的密钥管理要么是完全由用户端掌握密钥(如iPhone本地数据加密,密钥存在Secure Enclave中),要么是在用户许可下由苹果代管(如传统iCloud云备份未启用高级加密时,苹果保存备份密钥)。苹果并没有公开采用“两方门限”的模式来和用户分享密钥,否则等于声明“用户单方无法完全掌控自己的解密权”。如果苹果暗中采用门限签名让自己持有一份密钥碎片,本质上就是一种**变相密钥托管(Escrow)**行为。这样的做法会明显偏离苹果宣称的零后门立场,与其在隐私政策中反复强调的原则相违背。值得注意的是,苹果在其官方隐私声明中明确表示:“我们从未在任何产品或服务中创建过后门或万能解锁主密钥”apple.com。因此,从理论和实践双重层面来看,用户私钥与潜在后门密钥是难以在不被发现的情况下拆分存在的。任何试图将二者解耦的举措都会引起体系架构的异常,进而难逃专家法眼。
加密社区对后门的发现与审计
在当今的安全生态中,不存在“悄无声息的后门”。一旦厂商试图在加密方案中掺入后门密钥,全球的密码学社区和安全研究人员都有多种手段将其揪出。下面从几个方面概述社区常用的后门检测与审计方法:
-
开源协议分析:安全专家偏好开源的软件和协议,因为源码透明意味着任何可疑的算法修改、密钥处理流程都暴露在公众视野中。通过阅读和形式化分析公开的协议规范,研究者可以发现是否有多余的密钥交换步骤或异常的参数。例如,Signal通信协议的源代码和技术细节是完全公开的,全球专家曾多次审阅其实现,验证其端到端加密未存在后门linkedin.com。事实证明,公开透明带来的是更严苛的监督,任何隐秘加入的密钥参数都有可能被审计人员发现。正如业内人士所指出的,Signal 采用开放源码意味着安全专家可以独立审计其代码以核实安全性linkedin.com。类似地,许多现代加密库都会经过社区审视,以确保其中没有“暗门”。
-
逆向工程与二进制审计:对于闭源的软件(例如苹果自身的系统组件),安全研究者会运用逆向工程技术来分析应用的二进制代码和运行时行为。一旦苹果的加密实现存在未公开的密钥使用,比如在本地程序中引用了某个神秘常量或调用了隐藏的密钥解密函数,逆向工程往往能还原这些逻辑。专业团队通过调试、反编译、动态埋点等方式重现协议的握手过程,查看每一步骤所用的密钥材料。如果过程中出现与官方文档不符的环节(例如本应由用户设备生成的密钥却从外部获取),将立即引发怀疑。此外,安全社区定期举办的漏洞挖掘和破解挑战赛也扮演重要角色——顶尖黑客会竞相攻破苹果设备的加密层,并公开报告发现的问题。过去这些努力揭示了一些实现漏洞(如内存越界、0day攻击途径),但从未曝出“苹果预留万能密钥”之类的后门。一例典型事件是2017年有黑客成功解密了Secure Enclave固件以研究其中机理,结果证实即便取得固件代码,攻击者仍无法提取到任何用户密钥或后门凭证ciso.economictimes.indiatimes.com。这一结论进一步增强了业界对苹果加密实现中无后门的信心。
-
网络流量与协议行为分析:加密协议往往涉及设备与服务器的交互流程。研究人员会抓包和监控这些网络流量,分析协议握手时交换的消息格式和内容。如果苹果尝试在密钥协商时暗中插入自己的公钥或请求额外数据,流量分析将捕捉到异常的报文模式。例如,在正常的端到端加密通信中,设备之间交换彼此的公钥证书,不应有第三方公钥悄然出现。而所谓“幽灵用户”后门提案正是要求服务提供商在群聊中偷偷加入一个看不见的第三方公钥。这样的方案被广泛批评因为它破坏了用户验证通信对端身份的机制,需要服务器隐藏通知才能欺骗用户lawfaremedia.org。密码学家指出,这将削弱认证过程并带来新漏洞,因此难以在不被发现的情况下实施lawfaremedia.org。由此可见,通过流量异常识别潜在后门是切实可行的。当年的GCHQ“幽灵用户”建议一提出,就被包括苹果在内的业界联合抵制,47家机构和专家联名公开信指出该做法“对网络安全构成严重威胁”internetsociety.orgsilicon.co.uk,可见社区对这类后门手段有高度警惕性。
-
独立审计和信任链验证:许多安全敏感的加密功能会接受独立机构的审计,以建立公众信任。比如苹果的 iCloud 钥匙串(Keychain) 采用多层加密和信任链机制,其设计文档表明敏感信息的密钥始终需要Secure Enclave参与才能解锁techrepublic.com。有第三方评估指出,钥匙串中的私密数据即便保存在云端也是经过高强度加密的,任何人(包括苹果)都无法直接读取明文techrepublic.com。这一架构经过多轮外部安全会议研讨和学者研究,至今未出现被植入后门的迹象。同样,苹果设备中的 Secure Enclave 安全隔区 也多次成为学术研究和黑客大会的焦点。研究人员通过攻击Secure Enclave找出了少数漏洞(例如早期A7-A11芯片存在硬件级漏洞ciso.economictimes.indiatimes.comciso.economictimes.indiatimes.com),但这些漏洞只是实现瑕疵,并非有意留出的后门。实际上,正是这些公开的审计和破解挑战证明了Secure Enclave的设计初衷:即使攻击者获得硬件或固件访问权,仍无法提取出主密钥ciso.economictimes.indiatimes.com。学术界和白帽黑客社区通过反复的审查和渗透测试,为苹果的“零后门”承诺提供了有力的背书。换言之,加密社区的独立审计机制确保了任何后门都难以隐藏;只有经得起各方检验的系统,才能真正赢得用户信任。
综上所述,在强大的社区监督下,任何后门密钥的存在都会留下蛛丝马迹,并最终被曝光。无论是协议分析、逆向工程还是实网监测,多层次的手段使得厂商无法神不知鬼不觉地在成熟加密方案中藏入后门。这也是为什么苹果等公司反复强调没有后门:一旦撒谎,终将被揭穿,信用荡然无存。
iCloud 钥匙串信任链下的全局数据加密密钥(DEK)机制研究
苹果的高级数据保护(Advanced Data Protection)引入了端到端加密,将大部分 iCloud 数据的密钥仅存储在用户的受信设备上support.apple.com。在该机制下,每个用户的 iCloud 帐户针对各数据类别生成自己的“全局”数据加密密钥(Data Encryption Key, DEK),这些密钥受 iCloud 钥匙串的信任链机制保护。下面将详细探讨全局 DEK 的生成、分发与封装,多设备场景下的生命周期变化,以及苹果保障 DEK 安全和确保服务器从未获取明文 DEK 的技术手段。
全局 DEK 的生成、更新与轮换
初始生成:当用户首次在支持的设备上启用高级数据保护时(需运行 iOS 16.2、macOS 13.1 等新版系统,并开启双重认证),系统会在该设备上本地生成全局数据加密密钥。实际上,每个受端到端加密保护的 iCloud 服务(例如云备份、照片、笔记等)都有各自的 CloudKit 服务密钥对,其私钥用作该类别数据的主加密密钥support.apple.comsupport.apple.com。这些服务密钥使用安全随机算法在用户受信设备上创建,具有唯一性,并由设备的安全硬件保护。启用高级数据保护时,设备会将之前由苹果保存的云端密钥从苹果的硬件安全模块(HSM)中删除,并生成新的服务密钥,以改用仅存储在用户设备上的密钥来加密云端数据support.apple.comsupport.apple.com。这一过程确保全局 DEK(即各服务的新密钥)仅存在于用户受信设备上,苹果服务器端不再持有其副本。
是否变化及何时变化:在正常使用中,全局 DEK(各服务密钥)的私钥一经生成会保持稳定,用于持续加密解密用户数据,并不会频繁更换。唯有在特定事件下才会轮换或更新密钥,例如用户启用高级数据保护时系统触发的一次性密钥轮换,以及用户后来关闭高级数据保护或怀疑密钥泄露时的情况support.apple.com。苹果文档指出,当用户打开高级数据保护时,设备会启动异步密钥轮换操作,为此前存储于苹果服务器的每个服务创建新的服务密钥support.apple.com。新数据随后使用新密钥加密,旧密钥无法解密新数据support.apple.com。同样地,当用户关闭高级数据保护返回标准保护时,设备会将原本仅存于本地的新密钥上传回苹果HSM,并可恢复使用先前的旧密钥support.apple.com。因此,可以总结:初始启用高级保护时会生成并切换到新的全局 DEK,此后这些密钥保持不变;如用户关闭功能则恢复旧密钥;除非再次启用或发生安全事件,系统通常不会主动更换全局 DEK。
值得注意的是,在极端情况下如果用户怀疑密钥泄露或设备失窃,用户可以选择通过重置整个端到端加密环境(例如先关闭再重新开启高级数据保护)来触发新的 DEK 生成,从而保护云端数据安全。然而,此操作会要求所有设备重新加入信任链,并重新上传数据副本加密后存储。
多设备环境下 DEK 的分发与封装
信任链机制: 苹果使用 iCloud 钥匙串的信任链(又称同步圈,circle of trust)来在多设备间安全同步全局 DEK。启用了高级数据保护后,属于用户 Apple ID 的所有受信设备共同构成一个加密信任链,每台设备都有一对用于同步的非对称椭圆曲线密钥(如 P-384)support.apple.com。当第一台设备生成全局 DEK 后,它会将这些密钥加入自身的 iCloud 钥匙串保护域,并通过 CloudKit 安全地共享给用户的其他设备support.apple.com。具体而言,设备会维护一份受信设备的公钥列表,并使用自身的私钥对列表签名后存储于 iCloud;只有持有用户账户密码或设备私钥者才能读取或篡改这份列表support.apple.com。这一机制保证了只有经过用户授权加入信任链的设备才能获取 DEK,其余任何第三方(包括苹果服务器)都无法读取信任链中的密钥数据support.apple.com。
密钥传递与封装:在多设备场景下,每台设备都会持有全局 DEK(各服务私钥)的一个副本,但这些副本始终以安全加密形式封装后再传输和存储。例如,当用户新增一台受信设备时,新设备会生成自己的同步密钥对并向云端发出加入信任链的请求support.apple.com。已有的一台受信设备(通常是用户主动在其上同意新增设备)会验证该请求并通过 设备间安全信道 传输 DEK 副本给新设备support.apple.com。在此过程中,现有设备会利用新设备的公钥来加密封装 DEK,或双方通过椭圆曲线 Diffie-Hellman(ECDH)协商会话密钥来传递 DEK,从而确保只有目标新设备能解开密钥包装。苹果未公开具体用哪种算法封装,但业界常用方案包括 AES 密钥封装算法(AES-KW) 或 AES-GCM 算法 对会话密钥加密support.apple.comsupport.apple.com。可以推测,Apple 采用了符合 NIST 标准的 AES-256 算法对对称 DEK 进行二次加密包装,并结合设备的非对称密钥进行密钥交换/加密,以实现端到端的安全传递。
本地存储与保护:当设备接收到封装的 DEK 后,会在本地将其解密并安全保存于设备的 Keychain 中。所有 DEK 私钥仅存在于设备的安全隔区中,例如 iPhone 的密钥保存在 Data Protection 类钥匙串项下,并受 Secure Enclave 协处理器保护(访问需通过用户设备解锁)support.apple.com。这样设计保证即使设备遗失或被攻破,未解锁状态下设备上的 DEK 依然难以提取。总之,多设备环境下,每台受信设备都持有全局 DEK 副本,但始终通过端到端加密的方式同步与存储:传输过程中使用公钥加密/会话密钥,存储时依赖设备硬件密钥封装技术(如 Secure Enclave 提供的UID派生密钥)进一步加密,最大程度降低密钥泄露风险。
设备新增、移除与丢失场景下 DEK 和数据的生命周期
新设备加入: 当用户在新设备上登入 iCloud 并启用高级数据保护时,该设备无法直接访问云端受保护数据,需要首先加入信任链。加入流程包括:新设备生成自己的同步密钥对并将公钥提交给苹果云端(CloudKit)support.apple.com;苹果服务器将此请求传达给用户已有的一台受信设备上,提醒用户有新设备申请加入。用户在已有设备上批准请求(需输入密码或通过生物识别验证身份),之后已有设备会将新设备的公钥添加到信任链并再次用自己的私钥和账户密码派生密钥签署信任圈数据support.apple.com。随后,该已有设备通过上述安全信道,将全局 DEK 的加密副本传送给新设备support.apple.com。一旦新设备成功解密获得 DEK,它就加入了受信设备列表,可以像其他设备一样解密云端的端到端加密数据。整个过程确保只有获得用户明示批准的新设备才能获取 DEK support.apple.com。
设备移除与更换:当用户从 Apple ID 中移除某台设备,或设备被抹除/重置时,该设备将不再被视为信任链的一员。此时其他仍在线的受信设备会更新信任链状态,将该设备的身份从受信列表中剔除support.apple.com。需要强调的是,移除设备本身并不会导致全局 DEK 自动更改。被移除的设备虽曾持有 DEK 副本,但一旦不再受信,其无法从苹果服务器获取新的数据更新,而且由于设备已从账户移除或被抹掉,攻击者无法再借此解密云端后续的数据。苹果并未设定在每次设备变动时轮换密钥,这是出于实用性的考虑——频繁更换 DEK 将要求对云端大量数据重新加密,代价高昂。不过,若某台设备遗失且用户怀疑其本地密钥可能泄露,用户可以选择手动采取措施,例如从 iCloud 设置中移除此设备并重置高级数据保护(关闭再开启),从而生成新的 DEK,保护未来的数据安全。
云端数据影响: 当设备移除或失效时,云端已经加密的数据依旧由原来的 DEK 保护,并不会因为设备离开而重新加密。只要用户其他任一受信设备仍保存着该 DEK,便可继续访问此前的数据。被移除的设备由于缺失信任凭证,也无法再从服务器同步到后续新增或修改的任何机密数据(即使攻击者拥有其物理设备,由于密钥受 Secure Enclave 和设备密码保护,也难以提取support.apple.com)。因此,在多设备环境中,云端数据的可访问性取决于至少有一台受信设备存有对应 DEK。只要用户至少有一台设备或有效的恢复方式,数据就可解密使用;反之则数据陷于加密状态无法读取。
失去所有设备:高级数据保护要求用户在失去所有受信设备的极端情况下,借助预先设置的恢复机制取回 DEK。苹果强制要求启用该功能的用户提供至少一种账户恢复方法(例如指定恢复联系人或设置恢复密钥)support.apple.comsupport.apple.com。当用户所有设备均遗失或不可用时,只有通过这些恢复方式才能重获对数据的访问权。具体而言,如果用户提前设置了恢复密钥(一串随机生成的28位字符)并安全保存,那么此时用户可在新设备上登陆 Apple ID,并输入该恢复密钥来恢复数据。苹果服务器会将一份加密的 DEK 备份( escrow 记录 )下发到新设备,而新设备利用用户提供的恢复密钥将其解密,提取出全局 DEKsupport.apple.comsupport.apple.com。由于恢复密钥是由用户掌控、苹果不存储明文的要素,只有提供正确密钥的新设备才能解开 escrow 获得 DEK。在成功恢复后,新设备将重建信任链,并可以访问之前端到端加密的所有云端数据。
若用户选择的是恢复联系人,流程类似:用户联系预先设定的可信联系人,由联系人通过其苹果设备生成一个验证代码提供给用户。用户在新设备上输入该代码后,苹果同样将加密的 DEK 备份下发,新设备据此恢复密钥。整个恢复流程依然遵循端到端加密原则:苹果仅充当中转并验证权限,但并不知晓用户的实际 DEK 内容support.apple.com。
不可恢复的情况:如果用户既没有其他受信设备、又未设置任何恢复联系人或恢复密钥,那么全局 DEK 将无法找回,相应的云端数据也就永久处于加密不可读状态support.apple.com。苹果明确表示,若用户丢失所有设备且无恢复方式,公司无法帮助用户恢复这部分端到端加密的数据support.apple.com。这凸显了高级数据保护的一个权衡:安全性增强的同时,数据恢复的责任完全由用户自担。因此用户需谨慎管理受信设备和恢复选项,以避免陷入无法解密个人数据的境地。
DEK 安全性的密码学保障机制
苹果在高级数据保护与 iCloud 钥匙串架构中运用了多种密码学机制来保障 DEK 的机密性和完整性,包括密钥封装、密钥派生、硬件安全模块,以及严格的权限控制:
-
端到端加密与密钥层级化:如上所述,iCloud 采用分层密钥架构对数据加密。以 CloudKit 私有数据库为例,每位用户有一个顶层的 CloudKit 服务密钥对,其私钥用来保护下层对称密钥(如 Zone密钥、Record记录密钥等)
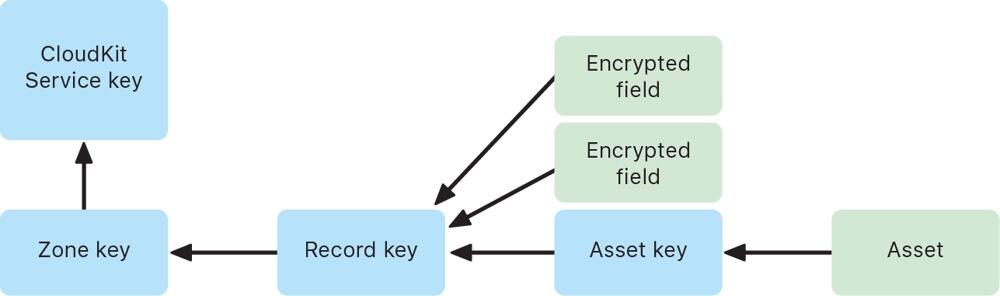 support.apple.com。当用户在设备上写入数据时,会生成记录级别的随机对称密钥加密数据字段,再逐层用上级密钥封装这些对称密钥。具体来说,记录密钥用 Zone 密钥加密,Zone 密钥再用全局服务公钥加密(即 DEK 公钥),形成多层密钥封装结构support.apple.com。只有持有最顶层私钥(DEK 私钥)的受信设备才能逐层解开封装,最终解密出用户数据。通过这种分层加密与密钥隔离设计,即使某一层的密钥泄露,攻击者也无法直接获取上层密钥或明文数据。
support.apple.com。当用户在设备上写入数据时,会生成记录级别的随机对称密钥加密数据字段,再逐层用上级密钥封装这些对称密钥。具体来说,记录密钥用 Zone 密钥加密,Zone 密钥再用全局服务公钥加密(即 DEK 公钥),形成多层密钥封装结构support.apple.com。只有持有最顶层私钥(DEK 私钥)的受信设备才能逐层解开封装,最终解密出用户数据。通过这种分层加密与密钥隔离设计,即使某一层的密钥泄露,攻击者也无法直接获取上层密钥或明文数据。 -
AES 密钥封装与封闭式硬件存储:苹果广泛采用了经验证的对称加密算法来封装和存储 DEK。传输过程中的 DEK(或下层对称密钥)通常通过 AES-256 算法加密封装后再上传support.apple.com。一种常用方法是 AES 密钥包装 (AES-KW),它专门用于用一个对称密钥安全地封装另一个密钥,确保密钥材料在传输中不暴露。与此同时,设备本地的 DEK 私钥会存储在受 Secure Enclave 保护的区域。Secure Enclave 为每台设备提供唯一的硬件 UID 密钥,仅用于解锁设备密钥袋和钥匙串项support.apple.com。也就是说, DEK 私钥本身可能被进一步用设备硬件密钥加密(这相当于在软件密钥之外又加了一道硬件锁)。只有当用户解锁设备并通过身份验证,操作系统才能调用 Secure Enclave 解封这些密钥用于加解密操作。通过AES-GCM 等对称加密结合Secure Enclave 硬件密钥封装,苹果确保 DEK 无论在云端传输还是本地存储,都始终处于加密状态,降低被截获或提取的风险support.apple.com。
-
椭圆曲线密码与密钥交换: 信任链中设备互认和密钥共享依赖椭圆曲线密码算法。每台设备的同步身份密钥对采用强大的 P-256 或 P-384 曲线support.apple.comsupport.apple.com。当新设备加入时,已有设备会利用椭圆曲线数字签名算法 (ECDSA) 对信任链数据签名校验,防止伪造support.apple.com。同时,在设备间传输 DEK 时,可能使用椭圆曲线 Diffie-Hellman (ECDH) 来建立共享密钥,加密传输内容。ECDH 可确保即使通信被窃听,攻击者无法推导出会话密钥,因而无法获取密钥内容。综上,非对称加密和密钥交换协议保证了只有合法设备才能参与密钥同步,新设备的引入需要现有设备用其私钥签名确认,杜绝中间人攻击或伪造信任链的可能。
-
密钥派生函数 (KDF):在某些步骤中,苹果使用了密钥派生函数强化密码。历史上,iCloud 钥匙串曾要求用户设置 iCloud 安全码时,将用户密码通过 PBKDF2 等KDF算法派生出密钥,用于签名和加密信任圈hackmag.comhackmag.com。即便在新的双重认证架构下,某些场景仍可能涉及KDF——例如恢复密钥或联系人代码很可能通过 KDF 转换为实际用于解密 escrow 密文的密钥材料。这些 KDF 算法引入高强度的盐值和大量迭代运算hackmag.com,增强了抗暴力破解能力,防止弱口令被攻击者猜测。总之,KDF 的应用确保从用户口令/恢复码到加密密钥的映射具有单向性和计算复杂度,进一步保护 DEK 相关流程的安全。
服务器无权获取明文 DEK 的保障
苹果的设计宗旨是在云端架起“盲墙”,确保服务器既无权也无实能接触用户 DEK 的明文,这也是实现“即使云端泄露,用户数据仍安全”的关键:
-
密钥仅存在于用户端: 开启高级数据保护后,所有主要 iCloud 数据类别的加密密钥仅存储于用户受信设备(或用户掌握的恢复载体)中,苹果服务器端不再保存这些密钥support.apple.com。文档明确指出,启用该功能后,苹果“无法读取或访问用户的服务密钥”support.apple.com。即在正常运行过程中,苹果的云服务器从未拥有解锁用户端到端加密数据所需的密钥。服务器所见到的只是由用户设备加密后的数据碎片,对其而言是不可解密的黑箱。
-
云端存储密文及加密元数据:iCloud 服务器虽然需要存储用户数据(如云照片、备忘录的加密内容),但这些内容均已由设备使用 DEK 加密完成。即便是为了提供某些功能,云端保留了少量未加密的元数据(如文件校验和用于重复数据消除),这些元数据也不包含可用于推导 DEK 的信息support.apple.comsupport.apple.com。苹果正在致力于将更多此类元数据也纳入端到端加密范围,以进一步减少明文暴露面support.apple.com。此外,CloudKit 框架要求开发者在模式中明确标记需要加密的字段,未标记的字段(例如排序用的时间戳)即便明文存储,亦不涉及敏感内容support.apple.com。由此,云服务器始终缺乏关于 DEK 或用户敏感数据的明文,一旦发生数据泄露或内部越权,攻击者拿到的也只是高强度加密下的乱码。
-
权限架构防范后门访问:苹果构建的信任链机制也防止了服务器假借授权来获取密钥的可能性。服务器不能私自添加受信设备或篡改信任链,因为每次信任链更新都需要现有设备的私钥签名以及(在老架构下)用户密码派生密钥的二次签名hackmag.comsupport.apple.com。苹果服务器既不持有用户设备私钥,也不知晓用户密码,因此无法伪造这些签名来诱导其他设备信任一个恶意设备。即使在双重认证体系下,服务器在设备加入流程中充当中继,并没有能力绕过用户批准直接将新设备植入圈内support.apple.comsupport.apple.com。这种架构等于为服务器访问用户密钥设置了密码学上的禁区。正如苹果安全白皮书所言,在最坏情形下如果用户丢失对 iCloud 钥匙串和其恢复机制的访问,那么相应的端到端加密数据苹果也无力恢复support.apple.com。苹果通过制度和技术结合,确保即便政府或机构要求提供用户数据,由于公司本身并无解密能力,只能交出加密的内容。
综上所述,Apple 高级数据保护下,全局数据加密密钥的生成由用户设备掌控,借助 iCloud 钥匙串信任链在多设备间安全同步。无论是在设备增加、移除还是用户失去设备的情况下,密钥和数据的生命周期管理均以用户掌控为中心:只要用户保有至少一个密钥载体(设备或恢复方式),数据即可解密使用;反之苹果也无法绕过用户获取密钥明文support.apple.com。苹果通过成熟的加密算法(AES-KW、ECDH 等)、硬件支持(Secure Enclave)、密钥分层与派生策略,实现了“零信任”云存储:服务器对用户密钥一无所知,从而使用户云端数据获得前所未有的保密性提升。
附录
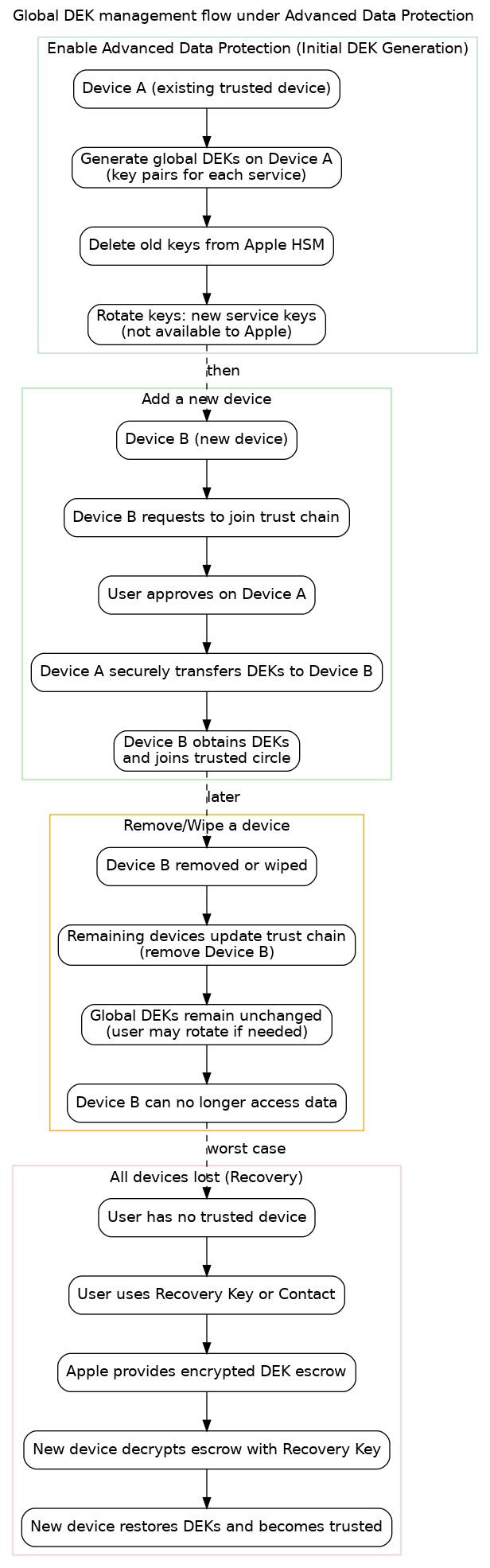 图:高级数据保护下全局 DEK 管理的流程示意图。包含初始启用(设备 A 上生成新密钥并删除苹果服务器密钥)、新设备加入信任链(设备 B 请求并由设备 A 批准传输密钥)、设备移除或丢失(更新信任列表,但密钥通常不变)、以及用户失去所有设备时的恢复流程(通过恢复密钥取回 DEK)。各阶段均保证 DEK 安全不被未授权实体获取。
图:高级数据保护下全局 DEK 管理的流程示意图。包含初始启用(设备 A 上生成新密钥并删除苹果服务器密钥)、新设备加入信任链(设备 B 请求并由设备 A 批准传输密钥)、设备移除或丢失(更新信任列表,但密钥通常不变)、以及用户失去所有设备时的恢复流程(通过恢复密钥取回 DEK)。各阶段均保证 DEK 安全不被未授权实体获取。 -
-
 @ 7460b7fd:4fc4e74b
2025-05-17 08:26:13
@ 7460b7fd:4fc4e74b
2025-05-17 08:26:13背景:WhatsApp的号码验证与运营商合作关系
作为一款基于手机号码注册的即时通信应用,WhatsApp的账号验证严重依赖全球电信运营商提供的短信或电话服务。这意味着,当用户注册或在新设备登录WhatsApp时,WhatsApp通常会向用户的手机号码发送SMS短信验证码或发起语音电话验证。这一流程利用了传统电信网络的基础设施,例如通过SS7(信令系统7)协议在全球范围内路由短信和电话securityaffairs.com。换句话说,WhatsApp把初始账户验证的安全性建立在电信运营商网络之上。然而,这种依赖关系也带来了隐患:攻击者可以利用电信网络的漏洞来拦截验证码。例如,研究人员早在2016年就演示过利用SS7协议漏洞拦截WhatsApp和Telegram的验证短信,从而劫持用户账户的攻击方法securityaffairs.com。由于SS7协议在全球范围内连接各国运营商,一个运营商的安全缺陷或恶意行为都可能被不法分子利用来获取他网用户的短信验证码securityaffairs.com。正因如此,有安全专家指出,仅依赖短信验证不足以保障账户安全,WhatsApp等服务提供商需要考虑引入额外机制来核实用户身份securityaffairs.com。
除了技术漏洞,基于电信运营商的验证还受到各地政策和网络环境影响。WhatsApp必须与全球各地运营商“合作”,才能将验证码送达到用户手机。然而这种“合作”在某些国家可能并不顺畅,典型例子就是中国。在中国大陆,国际短信和跨境电话常受到严格管控,WhatsApp在发送验证码时可能遭遇拦截或延迟sohu.com。因此,理解WhatsApp在中国的特殊联网和验证要求,需要将其全球验证机制与中国的电信政策和网络审查环境联系起来。下文将深入探讨为什么在中国使用WhatsApp进行号码验证时,必须开启蜂窝移动数据,并分析其中的技术逻辑和政策因素。
中国环境下的特殊问题:为何必须开启蜂窝数据?
中国的网络审查与封锁: WhatsApp自2017年起就在中国大陆遭遇严格封锁。起初,WhatsApp在华的服务受到**“GFW”(防火长城)**的部分干扰——例如曾一度只能发送文本消息,语音、视频和图片消息被封锁theguardian.com。到2017年下半年,封锁升级,很多用户报告在中国完全无法使用WhatsApp收发任何消息theguardian.com。中国官方将WhatsApp与Facebook、Telegram等西方通信平台一同屏蔽,视作对国家网络主权的挑战theguardian.com。鉴于此,在中国境内直接访问WhatsApp的服务器(无论通过Wi-Fi还是本地互联网)都会被防火长城所阻断。即使用户收到了短信验证码,WhatsApp客户端也无法在没有特殊连接手段的情况下与服务器完成验证通信。因此,单纯依赖Wi-Fi等本地网络环境往往无法完成WhatsApp的注册或登陆。很多用户经验表明,在中国使用WhatsApp时需要借助VPN等工具绕过审查,同时尽可能避免走被审查的网络路径sohu.com。
强制Wi-Fi热点与连接策略: 除了国家级的封锁,用户所连接的局域网络也可能影响WhatsApp验证。许多公共Wi-Fi(如机场、商场)采取强制门户认证(captive portal),用户需登录认证后才能上网。对此,WhatsApp在客户端内置了检测机制,当发现设备连入这类强制Wi-Fi热点而无法访问互联网时,会提示用户忽略该Wi-Fi并改用移动数据faq.whatsapp.com。WhatsApp要求对此授予读取Wi-Fi状态的权限,以便在检测到被拦截时自动切换网络faq.whatsapp.com。对于中国用户来说,即便所连Wi-Fi本身联网正常,由于GFW的存在WhatsApp依然可能视之为“不通畅”的网络环境。这也是WhatsApp官方指南中强调:如果Wi-Fi网络无法连接WhatsApp服务,应直接切换到手机的移动数据网络faq.whatsapp.com。在中国,由于本地宽带网络对WhatsApp的封锁,蜂窝数据反而成为相对可靠的通道——尤其在搭配VPN时,可以避开本地ISP的审查策略,实现与WhatsApp服务器的通信sohu.com。
国际短信的运营商限制: 使用移动数据还有助于解决短信验证码接收难题。中国的手机运营商出于防垃圾短信和安全考虑,默认对国际短信和境外来电进行一定限制。许多中国用户发现,注册WhatsApp时迟迟收不到验证码短信,原因可能在于运营商将来自国外服务号码的短信拦截或过滤sohu.com。例如,中国移动默认关闭国际短信接收,需要用户主动发送短信指令申请开通sohu.com。具体而言,中国移动用户需发送文本“11111”到10086(或10085)来开通国际短信收发权限;中国联通和电信用户也被建议联系运营商确认未屏蔽国际短信sohu.com。若未进行这些设置,WhatsApp发送的验证码短信可能根本无法抵达用户手机。在这种情况下,WhatsApp提供的备用方案是语音电话验证,即通过国际电话拨打用户号码并播报验证码。然而境外来电在中国也可能遭到运营商的安全拦截,特别是当号码被认为可疑时zhuanlan.zhihu.com。因此,中国用户经常被建议开启手机的蜂窝数据和漫游功能,以提高验证码接收的成功率sohu.com。一方面,开启数据漫游意味着用户准备接受来自境外的通信(通常也包含短信/电话);另一方面,在数据联网的状态下,WhatsApp可以尝试通过网络直接完成验证通信,从而减少对SMS的依赖。
移动数据的网络路径优势: 在实际案例中,一些中国WhatsApp用户报告仅在开启蜂窝数据的情况下才能完成验证。这可能归因于蜂窝网络和宽带网络在国际出口上的差异。中国移动、联通等运营商的移动数据可能走与宽带不同的网关路由,有时对跨境小流量的拦截相对宽松。此外,WhatsApp在移动数据环境中可以利用一些底层网络特性。例如,WhatsApp可能通过移动网络发起某些专用请求或利用运营商提供的号码归属地信息进行辅助验证(虽然具体实现未公开,但这是业界讨论的可能性)。总之,在中国特殊的网络环境下,开启蜂窝数据是确保WhatsApp验证流程顺利的重要一步。这一步不仅是为了基本的互联网连接,也是为了绕开种种对国际短信和应用数据的拦截限制,从而与WhatsApp的全球基础设施建立必要的通讯。
PDP Context与IMSI:移动网络验证的技术细节
要理解为什么移动数据对WhatsApp验证如此关键,有必要了解移动通信网络中的一些技术细节,包括PDP Context和IMSI的概念。
PDP Context(分组数据协议上下文): 当手机通过蜂窝网络使用数据(如4G/5G上网)时,必须先在运营商核心网中建立一个PDP上下文。这实际上就是申请开启一个数据会话,运营商将为设备分配一个IP地址,并允许其通过移动核心网访问互联网datascientest.com。PDP上下文包含了一系列参数(例如APN接入点名称、QoS等级等),描述该数据会话的属性datascientest.comdatascientest.com。简单来说,激活蜂窝数据就意味着创建了PDP上下文,设备获得了移动网络网关分配的IP地址,可以收发数据包。对于WhatsApp验证而言,只有在建立数据连接后,手机才能直接与WhatsApp的服务器交换数据,例如提交验证码、完成加密密钥协商等。如果仅有Wi-Fi而蜂窝数据关闭,且Wi-Fi环境无法连通WhatsApp服务器,那么验证过程将陷入停滞。因此,在中国场景下,开启蜂窝数据(即建立PDP数据通路)是WhatsApp客户端尝试绕过Wi-Fi限制、直接通过移动网络进行验证通信的前提faq.whatsapp.comsohu.com。值得一提的是,PDP Context的建立也表明手机在运营商网络上处于活跃状态,这对于某些验证机制(比如后述的闪信/闪呼)来说至关重要。
IMSI与MSISDN: IMSI(国际移动用户标识)和MSISDN(移动用户号码,即手机号码)是运营商网络中两个密切相关但不同的标识。IMSI是存储在SIM卡上的一串唯一数字,用于在移动网络中标识用户身份netmanias.com。当手机接入网络时,它向运营商提供IMSI以进行鉴权,运营商据此知道“是哪张SIM”的请求netmanias.com。而MSISDN则是我们平常说的手机号,用于在语音通话和短信路由中定位用户,也存储在运营商的HLR/HSS数据库中netmanias.com。运营商通过IMSI<->MSISDN的对应关系,将来自全球的短信/电话正确路由到用户手机上。WhatsApp的验证短信或电话本质上就是通过目标号码(MSISDN)寻找所属运营商网络,由该网络根据IMSI定位用户终端。一般情况下,WhatsApp应用并不直接接触IMSI这种信息,因为IMSI属于运营商网络的内部标识。然而,IMSI的存在仍然对安全产生影响。例如,**SIM卡交换(SIM Swap)**欺诈发生时,攻击者获得了受害者号码的新SIM卡,新SIM卡会有不同的IMSI,但MSISDN保持原号码不变。运营商会将原号码映射到新的IMSI,这样验证码短信就发送到了攻击者手中的SIM上。对WhatsApp而言,除非有机制检测IMSI变动,否则无法察觉用户号码背后的SIM已被盗换。部分应用在检测到SIM变化时会提示用户重新验证,这需要读取设备的IMSI信息进行比对。然而,在现代智能手机中,获取IMSI通常需要特殊权限,WhatsApp并未明确说明它有此类检测。因此,从WhatsApp角度,IMSI更多是网络侧的概念,但它提醒我们:电信级身份验证依赖于SIM的有效性。只有当正确的IMSI在网络注册、并建立了PDP数据上下文时,WhatsApp的后台服务才能确认该SIM对应的号码目前“在线”,进而可靠地发送验证信号(短信或电话)到该设备。
移动网络的信号辅助验证: 有观点认为,一些OTT应用可能利用移动网络提供的附加服务来辅助号码验证。例如,某些运营商提供号码快速验证API,当应用检测到设备在移动数据网络中时,可以向特定地址发起请求,由运营商返回当前设备的号码信息(通常通过已经建立的PDP通道)。Google等公司在部分国家与运营商合作过类似服务,实现用户免输入验证码自动完成验证。但就WhatsApp而言,没有公开证据表明其使用了运营商提供的自动号码识别API。即便如此,WhatsApp鼓励用户保持移动网络在线的做法,隐含的意义之一可能是:当手机处于蜂窝网络且数据畅通时,验证码通过率和验证成功率都会显著提升。这既包括了物理层面短信、电话能否送达,也涵盖了数据层面应用和服务器能否互通。
Flash Call机制:WhatsApp验证的新方案
针对传统SMS验证码容易被拦截、延迟以及用户体验不佳的问题,WhatsApp近年来引入了一种Flash Call(闪呼)验证机制fossbytes.com。所谓闪呼,即应用在用户验证阶段向用户的手机号发起一个非常短暂的来电:用户无需真正接听,WhatsApp会自动结束这通电话,并根据通话记录来确认是否拨通fossbytes.com。
原理与流程: 当用户选择使用闪呼验证(目前主要在Android设备上可用),WhatsApp会请求权限访问用户的通话记录fossbytes.com。随后应用拨打用户的号码,一般是一个预先设定的特定号码或号码段。由于WhatsApp后台知道它拨出的号码及通话ID,只要该未接来电出现在用户手机的通话日志中,应用即可读取并匹配最后一通来电的号码是否符合验证要求,从而确认用户持有这个号码fossbytes.com。整个过程用户无需手动输入验证码,验证通话在数秒内完成。相比6位数字短信验证码需要用户在短信和应用间切换输入,闪呼方式更加快捷无缝fossbytes.com。
优缺点分析: 闪呼验证的优势在于速度快且避免了SMS可能的延迟或拦截。一些分析指出闪呼将成为取代SMS OTP(一次性密码)的新趋势,Juniper Research预测2022年用于验证的闪呼次数将从2021年的六千万猛增到五十亿次subex.comglobaltelcoconsult.com。对于WhatsApp这样全球用户庞大的应用,闪呼可以节约大量SMS网关费用,并绕开部分运营商对国际SMS的限制。然而,闪呼也有局限:fossbytes.com首先,iOS设备由于系统安全限制,应用无法访问通话记录,因此iPhone上无法使用闪呼验证fossbytes.com。这意味着苹果用户仍需使用传统短信验证码。其次,为实现自动匹配来电号码,用户必须授予读取通话记录的权限,这在隐私上引发一些担忧fossbytes.comfossbytes.com。WhatsApp声称不会将通话记录用于验证以外的用途,号码匹配也在本地完成fossbytes.com,但考虑到母公司Meta的隐私争议,部分用户依然顾虑。第三,闪呼验证依赖语音通话路线,同样受制于电信网络质量。如果用户所处网络无法接通国际来电(比如被运营商拦截境外短振铃电话),闪呼也无法成功。此外,从运营商角度看,闪呼绕过了A2P短信计费,可能侵蚀短信营收,一些运营商开始研究识别闪呼流量的策略wholesale.orange.com。总体而言,闪呼机制体现了WhatsApp希望减轻对短信依赖的努力,它在许多国家提升了验证体验,但在中国等特殊环境,其效果仍取决于本地语音网络的开放程度。值得注意的是,中国运营商对于境外电话,尤其是这种**“零响铃”未接来电**也有防范措施,中国电信和联通用户就被建议如需接收海外来电验证,应联系客服确保未拦截海外来电hqsmartcloud.com。因此,即便WhatsApp支持闪呼,中国用户若未开启移动语音漫游或运营商许可,仍然难以通过此途径完成验证。
与SIM Swap安全性的关系: 从安全角度看,闪呼并未实质提升抵御SIM交换攻击的能力。如果攻击者成功将受害者的号码转移至自己的SIM卡上(获取新IMSI),那么无论验证码以短信还是闪呼方式发送,都会到达攻击者设备。闪呼机制能防御的是部分恶意拦截短信的行为(如恶意网关或木马读取短信),但对社工换卡没有太大帮助。WhatsApp早已提供两步验证(即设置6位PIN码)供用户自行启用,以防号码被他人重新注册时需要额外密码。然而大量用户未开启该功能。因此,闪呼更多是从用户体验和成本出发的改良,而非针对高级别攻击的防护机制。正如前文所述,真正要防御SIM Swap和SS7漏洞等系统性风险,依赖运营商的号码验证本身就是薄弱环节,需要引入更高级的身份认证手段。
SIM卡交换攻击的风险与运营商信任问题
WhatsApp和Telegram一类基于手机号认证的应用普遍面临一个安全挑战:手机号码本身并非绝对安全的身份凭证。攻击者可以通过一系列手段取得用户的号码控制权,其中SIM交换(SIM Swap)是近年高发的欺诈手法。SIM Swap通常由不法分子冒充用户,诱骗或贿赂运营商客服将目标号码的服务转移到攻击者的新SIM卡上keepnetlabs.com。一旦成功,所有发往该号码的短信和电话都转由攻击者接收,原机主的SIM卡失效。对于依赖短信/电话验证的应用来说,这意味着攻击者可以轻易获取验证码,从而重置账户并登录。近年来全球SIM Swap案件呈上升趋势,许多在线服务的账号被此攻破rte.ie。
WhatsApp并非未知晓此风险。事实上,WhatsApp在其帮助中心和安全博客中多次提醒用户开启两步验证PIN,并强调绝不向他人透露短信验证码。然而,从系统设计上讲,WhatsApp仍将信任根基放在运营商发送到用户手机的那串数字验证码上。一旦运营商端的安全被绕过(无论是内部员工作恶、社工欺诈,还是SS7网络被黑客利用securityaffairs.com),WhatsApp本身无法辨别验证码接收者是否是真正的用户。正如安全研究所Positive Technologies指出的那样,目前主要的即时通讯服务(包括WhatsApp和Telegram)依赖SMS作为主要验证机制,这使得黑客能够通过攻击电信信令网络来接管用户账户securityaffairs.com。换言之,WhatsApp被迫信任每一个参与短信/电话路由的运营商,但这个信任链条上任何薄弱环节都可能遭到利用securityaffairs.com。例如,在SIM Swap攻击中,运营商本身成为被欺骗的对象;而在SS7定位拦截攻击中,全球互联的电信网成为攻击面。在中国的场景下,虽然主要威胁来自审查而非黑客,但本质上仍是WhatsApp无法完全掌控电信网络这一事实所导致的问题。
应对这些风险,WhatsApp和Telegram等采用了一些弥补措施。除了提供用户自行设定的二次密码,两者也开始探索设备多因子的概念(如后文Telegram部分所述,利用已有登录设备确认新登录)。然而,对绝大多数首次注册或更换设备的用户来说,传统的短信/电话验证仍是唯一途径。这就是为什么在高安全需求的行业中,SMS OTP正逐渐被视为不充分securityaffairs.com。监管机构和安全专家建议对涉敏感操作采用更强验证,如专用身份应用、硬件令牌或生物识别等。WhatsApp作为大众通信工具,目前平衡了易用性与安全性,但其依赖电信运营商的验证模式在像中国这样特殊的环境下,既遇到政策阻碍,也隐藏安全短板。这一点对于决策制定者评估国外通信应用在华风险时,是一个重要考量:任何全球运营商合作机制,在中国境内都可能因为**“最后一公里”由中国运营商执行**而受到影响。无论是被拦截信息还是可能的监控窃听,这些风险都源自于底层通信网的控制权不在应用服务商手中。
Telegram登录机制的比较
作为对比,Telegram的账号登录机制与WhatsApp类似,也以手机号码为主要身份标识,但在具体实现上有一些不同之处。
多设备登录与云端代码: Telegram从设计上支持多设备同时在线(手机、平板、PC等),并将聊天内容储存在云端。这带来的一个直接好处是:当用户在新设备上登录时,Telegram会优先通过已登录的其他设备发送登录验证码。例如,用户尝试在电脑上登录Telegram,Telegram会在用户手机上的Telegram应用里推送一条消息包含登录码,而不是立即发短信accountboy.comaccountboy.com。用户只需在新设备输入从老设备上收到的代码即可完成登录。这种机制确保了只要用户至少有一个设备在线,就几乎不需要依赖运营商短信。当然,如果用户当前只有一部新设备(例如换了手机且旧设备不上线),Telegram才会退而求其次,通过SMS发送验证码到手机号。同时,Telegram也允许用户选择语音电话获取验证码,类似于WhatsApp的语音验证。当用户完全无法收到SMS时(比如在中国这种场景),语音呼叫常常比短信更可靠seatuo.com。
两步验证密码: 与WhatsApp一样,Telegram提供可选的两步验证密码。当启用此功能后,即使拿到短信验证码,仍需输入用户设置的密码才能登录账户quora.com。这对抗SIM Swap等攻击提供了另一层防线。不过需要指出,如果用户忘记了设置的Telegram密码且没有设置信任邮箱,可能会永久失去账号访问,因此开启该功能在中国用户中接受度一般。
登录体验与安全性的取舍: Telegram的登录流程在用户体验上更加灵活。多设备下无需每次都收验证码,提高了便利性。但从安全角度看,这种“信任已有设备”的做法也有隐患:如果用户的某个设备落入他人之手并未及时登出,那么该人有可能利用该设备获取新的登录验证码。因此Telegram会在应用中提供管理活动会话的功能,用户可随时查看和撤销其它设备的登录状态telegram.org。总体而言,Telegram和WhatsApp在初始注册环节同样依赖短信/电话,在这一点上,中国的网络环境对两者影响相似:Telegram在中国同样被全面封锁,需要VPN才能使用,其短信验证码发送也会受到运营商限制。另外,Telegram曾在2015年因恐怖分子利用该平台传递信息而被中国当局重点关注并屏蔽,因此其国内可达性甚至比WhatsApp更低。许多中国用户实际使用Telegram时,通常绑定国外号码或通过海外SIM卡来收取验证码,以绕开国内运营商的限制。
差异总结: 简而言之,Telegram在登录验证机制上的主要优势在于已有会话协助和云端同步。这使得老用户换设备时不依赖国内短信通道即可登录(前提是原设备已登录并可访问)。WhatsApp直到最近才推出多设备功能,但其多设备模式采用的是端到端加密设备链路,需要主手机扫码授权,而非像Telegram那样用账号密码登录其它设备。因此WhatsApp仍然强绑定SIM卡设备,首次注册和更换手机号时逃不开运营商环节。安全方面,两者的SMS验证所面临的系统性风险(如SS7攻击、SIM Swap)并无本质区别,都必须仰仗运营商加强对核心网络的保护,以及用户自身启用附加验证措施securityaffairs.comkeepnetlabs.com。
结论
对于希望在中国使用WhatsApp的用户来说,“开启蜂窝数据”这一要求背后体现的是技术与政策交织的复杂现实。一方面,蜂窝数据承载着WhatsApp与其全球服务器通信的关键信道,在中国的受限网络中提供了相对可靠的出路faq.whatsapp.comsohu.com。另一方面,WhatsApp的号码验证机制深深植根于传统电信体系,必须经由全球运营商的“协作”才能完成用户身份确认securityaffairs.com。而在中国,这种协作受到防火长城和运营商政策的双重阻碍:国际短信被拦截、国际数据被阻断。为克服这些障碍,WhatsApp既采取了工程上的应对(如检测强制Wi-Fi并提示使用移动网络faq.whatsapp.com),也引入了诸如闪呼验证等新方案以减少对短信的依赖fossbytes.com。但从根本上说,只要注册流程离不开手机号码,这种与电信运营商的捆绑关系就无法割舍。由此带来的安全问题(如SIM Swap和信令网络漏洞)在全球范围内敲响警钟securityaffairs.comkeepnetlabs.com。
对于从事安全研究和政策评估的人士,这篇分析揭示了WhatsApp在中国遇到的典型困境:技术系统的全球化与监管环境的本地化冲突。WhatsApp全球统一的验证框架在中国水土不服,不得不通过额外的设置和手段来“曲线救国”。这既包括让用户切换网络、配置VPN等绕过审查,也包括思考未来是否有必要采用更安全独立的验证方式。相比之下,Telegram的机制给出了一种启示:灵活运用多设备和云服务,至少在一定程度上降低对单一短信渠道的依赖。然而,Telegram自身在中国的处境表明,再优雅的技术方案也难以直接对抗高强度的网络封锁。最终,无论是WhatsApp还是Telegram,要想在受限环境下可靠运作,都需要技术与政策的双管齐下:一方面提高验证与登录的安全性和多样性,另一方面寻求运营商和监管层面的理解与配合。
综上所述,WhatsApp要求中国用户开启蜂窝数据并非偶然的臆想,而是其全球运营商合作验证机制在中国受阻后的务实选择。这一要求折射出移动通信应用在跨境运营中面临的挑战,也提醒我们在设计安全策略时必须考虑底层依赖的信任假设。对于个人用户,最实际的建议是在使用此类应用时提前了解并遵循这些特殊设置(如开通国际短信、启用数据漫游),并善用应用自身的安全功能(如两步验证)来保护账户免遭社工和网络攻击keepnetlabs.com。对于监管和运营商,则有必要权衡安全审查与用户便利之间的平衡,在可控范围内为可信的全球服务留出技术通道。在全球通信愈加融合的时代,WhatsApp的中国验证问题或许只是一个缩影,背后涉及的既有网络安全考量,也有数字主权与国际合作的议题,值得持续深入研究和关注。
faq.whatsapp.comfossbytes.comtheguardian.comsecurityaffairs.comsecurityaffairs.comkeepnetlabs.comdatascientest.comnetmanias.comsohu.comsohu.com
-
 @ 472f440f:5669301e
2025-05-20 02:00:54
@ 472f440f:5669301e
2025-05-20 02:00:54Marty's Bent
https://www.youtube.com/watch?v=p0Sj1sG05VQ
Here's a great presentation from our good friend nostr:nprofile1qyx8wumn8ghj7cnjvghxjmcpp4mhxue69uhkummn9ekx7mqqyz2hj3zg2g3pqwxuhg69zgjhke4pcmjmmdpnndnefqndgqjt8exwj6ee8v7 , President of The Nakamoto Institute titled Hodl for Good. He gave it earlier this year at the BitBlockBoom Conference, and I think it's something everyone reading this should take 25 minutes to watch. Especially if you find yourself wondering whether or not it's a good idea to spend bitcoin at any given point in time. Michael gives an incredible Austrian Economics 101 lesson on the importance of lowering one's time preference and fully understanding the importance of hodling bitcoin. For the uninitiated, it may seem that the hodl meme is nothing more than a call to hoard bitcoins in hopes of getting rich eventually. However, as Michael points out, there's layers to the hodl meme and the good that hodling can bring individuals and the economy overall.
The first thing one needs to do to better understand the hodl meme is to completely flip the framing that is typically thrust on bitcoiners who encourage others to hodl. Instead of ceding that hodling is a greedy or selfish action, remind people that hodling, or better known as saving, is the foundation of capital formation, from which all productive and efficient economic activity stems. Number go up technology is great and it really matters. It matters because it enables anybody leveraging that technology to accumulate capital that can then be allocated toward productive endeavors that bring value to the individual who creates them and the individual who buys them.
When one internalizes this, it enables them to turn to personal praxis and focus on minimizing present consumption while thinking of ways to maximize long-term value creation. Live below your means, stack sats, and use the time that you're buying to think about things that you want in the future. By lowering your time preference and saving in a harder money you will have the luxury of demanding higher quality goods in the future. Another way of saying this is that you will be able to reshape production by voting with your sats. Initially when you hold them off the market by saving them - signaling that the market doesn't have goods worthy of your sats - and ultimately by redeploying them into the market when you find higher quality goods that meet the standards desire.
The first part of this equation is extremely important because it sends a signal to producers that they need to increase the quality of their work. As more and more individuals decide to use bitcoin as their savings technology, the signal gets stronger. And over many cycles we should begin to see low quality cheap goods exit the market in favor of higher quality goods that provide more value and lasts longer and, therefore, make it easier for an individual to depart with their hard-earned and hard-saved sats. This is only but one aspect that Michael tries to imbue throughout his presentation.
The other is the ability to buy yourself leisure time when you lower your time preference and save more than you spend. When your savings hit a critical tipping point that gives you the luxury to sit back and experience true leisure, which Michael explains is not idleness, but the contemplative space to study, create art, refine taste, and to find what "better goods" actually are. Those who can experience true leisure while reaping the benefits of saving in a hard asset that is increasing in purchasing power significantly over the long term are those who build truly great things. Things that outlast those who build them. Great art, great monuments, great institutions were all built by men who were afforded the time to experience leisure. Partly because they were leveraging hard money as their savings and the place they stored the profits reaped from their entrepreneurial endeavors.
If you squint and look into the future a couple of decades, it isn't hard to see a reality like this manifesting. As more people begin to save in Bitcoin, the forces of supply and demand will continue to come into play. There will only ever be 21 million bitcoin, there are around 8 billion people on this planet, and as more of those 8 billion individuals decide that bitcoin is the best savings vehicle, the price of bitcoin will rise.
When the price of bitcoin rises, it makes all other goods cheaper in bitcoin terms and, again, expands the entrepreneurial opportunity. The best part about this feedback loop is that even non-holders of bitcoin benefit through higher real wages and faster tech diffusion. The individuals and business owners who decide to hodl bitcoin will bring these benefits to the world whether you decide to use bitcoin or not.
This is why it is virtuous to hodl bitcoin. The potential for good things to manifest throughout the world increase when more individuals decide to hodl bitcoin. And as Michael very eloquently points out, this does not mean that people will not spend their bitcoin. It simply means that they have standards for the things that they will spend their bitcoin on. And those standards are higher than most who are fully engrossed in the high velocity trash economy have today.
In my opinion, one of those higher causes worthy of a sats donation is nostr:nprofile1qyfhwumn8ghj7enjv4jhyetvv9uju7re0gq3uamnwvaz7tmfdemxjmrvv9nk2tt0w468v6tvd3skwefwvdhk6qpqwzc9lz2f40azl98shkjewx3pywg5e5alwqxg09ew2mdyeey0c2rqcfecft . Consider donating so they can preserve and disseminate vital information about bitcoin and its foundations.
The Shell Game: How Health Narratives May Distract from Vaccine Risks
In our recent podcast, Dr. Jack Kruse presented a concerning theory about public health messaging. He argues that figures like Casey and Callie Means are promoting food and exercise narratives as a deliberate distraction from urgent vaccine issues. While no one disputes healthy eating matters, Dr. Kruse insists that focusing on "Froot Loops and Red Dye" diverts attention from what he sees as immediate dangers of mRNA vaccines, particularly for children.
"It's gonna take you 50 years to die from processed food. But the messenger jab can drop you like Damar Hamlin." - Dr Jack Kruse
Dr. Kruse emphasized that approximately 25,000 children per month are still receiving COVID vaccines despite concerns, with 3 million doses administered since Trump's election. This "shell game," as he describes it, allows vaccines to remain on childhood schedules while public attention fixates on less immediate health threats. As host, I believe this pattern deserves our heightened scrutiny given the potential stakes for our children's wellbeing.
Check out the full podcast here for more on Big Pharma's alleged bioweapons program, the "Time Bank Account" concept, and how Bitcoin principles apply to health sovereignty.
Headlines of the Day
Aussie Judge: Bitcoin is Money, Possibly CGT-Exempt - via X
JPMorgan to Let Clients Buy Bitcoin Without Direct Custody - via X
Get our new STACK SATS hat - via tftcmerch.io
Mubadala Acquires 384,239 sats | $408.50M Stake in BlackRock Bitcoin ETF - via X
Take the First Step Off the Exchange
Bitkey is an easy, secure way to move your Bitcoin into self-custody. With simple setup and built-in recovery, it’s the perfect starting point for getting your coins off centralized platforms and into cold storage—no complexity, no middlemen.
Take control. Start with Bitkey.
Use the promo code “TFTC20” during checkout for 20% off
Ten31, the largest bitcoin-focused investor, has deployed 158,469 sats | $150.00M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/invest.
Final thought...
I've been walking from my house around Town Lake in Austin in the mornings and taking calls on the walk. Big fan of a walking call.
Get this newsletter sent to your inbox daily: https://www.tftc.io/bitcoin-brief/
Subscribe to our YouTube channels and follow us on Nostr and X:
-
 @ c1e9ab3a:9cb56b43
2025-05-18 04:14:48
@ c1e9ab3a:9cb56b43
2025-05-18 04:14:48Abstract
This document proposes a novel architecture that decouples the peer-to-peer (P2P) communication layer from the Bitcoin protocol and replaces or augments it with the Nostr protocol. The goal is to improve censorship resistance, performance, modularity, and maintainability by migrating transaction propagation and block distribution to the Nostr relay network.
Introduction
Bitcoin’s current architecture relies heavily on its P2P network to propagate transactions and blocks. While robust, it has limitations in terms of flexibility, scalability, and censorship resistance in certain environments. Nostr, a decentralized event-publishing protocol, offers a multi-star topology and a censorship-resistant infrastructure for message relay.
This proposal outlines how Bitcoin communication could be ported to Nostr while maintaining consensus and verification through standard Bitcoin clients.
Motivation
- Enhanced Censorship Resistance: Nostr’s architecture enables better relay redundancy and obfuscation of transaction origin.
- Simplified Lightweight Nodes: Removing the full P2P stack allows for lightweight nodes that only verify blockchain data and communicate over Nostr.
- Architectural Modularity: Clean separation between validation and communication enables easier auditing, upgrades, and parallel innovation.
- Faster Propagation: Nostr’s multi-star network may provide faster propagation of transactions and blocks compared to the mesh-like Bitcoin P2P network.
Architecture Overview
Components
-
Bitcoin Minimal Node (BMN):
- Verifies blockchain and block validity.
- Maintains UTXO set and handles mempool logic.
- Connects to Nostr relays instead of P2P Bitcoin peers.
-
Bridge Node:
- Bridges Bitcoin P2P traffic to and from Nostr relays.
- Posts new transactions and blocks to Nostr.
- Downloads mempool content and block headers from Nostr.
-
Nostr Relays:
- Accept Bitcoin-specific event kinds (transactions and blocks).
- Store mempool entries and block messages.
- Optionally broadcast fee estimation summaries and tipsets.
Event Format
Proposed reserved Nostr
kindnumbers for Bitcoin content (NIP/BIP TBD):| Nostr Kind | Purpose | |------------|------------------------| | 210000 | Bitcoin Transaction | | 210001 | Bitcoin Block Header | | 210002 | Bitcoin Block | | 210003 | Mempool Fee Estimates | | 210004 | Filter/UTXO summary |
Transaction Lifecycle
- Wallet creates a Bitcoin transaction.
- Wallet sends it to a set of configured Nostr relays.
- Relays accept and cache the transaction (based on fee policies).
- Mining nodes or bridge nodes fetch mempool contents from Nostr.
- Once mined, a block is submitted over Nostr.
- Nodes confirm inclusion and update their UTXO set.
Security Considerations
- Sybil Resistance: Consensus remains based on proof-of-work. The communication path (Nostr) is not involved in consensus.
- Relay Discoverability: Optionally bootstrap via DNS, Bitcoin P2P, or signed relay lists.
- Spam Protection: Relay-side policy, rate limiting, proof-of-work challenges, or Lightning payments.
- Block Authenticity: Nodes must verify all received blocks and reject invalid chains.
Compatibility and Migration
- Fully compatible with current Bitcoin consensus rules.
- Bridge nodes preserve interoperability with legacy full nodes.
- Nodes can run in hybrid mode, fetching from both P2P and Nostr.
Future Work
- Integration with watch-only wallets and SPV clients using verified headers via Nostr.
- Use of Nostr’s social graph for partial trust assumptions and relay reputation.
- Dynamic relay discovery using Nostr itself (relay list events).
Conclusion
This proposal lays out a new architecture for Bitcoin communication using Nostr to replace or augment the P2P network. This improves decentralization, censorship resistance, modularity, and speed, while preserving consensus integrity. It encourages innovation by enabling smaller, purpose-built Bitcoin nodes and offloading networking complexity.
This document may become both a Bitcoin Improvement Proposal (BIP-XXX) and a Nostr Improvement Proposal (NIP-XXX). Event kind range reserved: 210000–219999.
-
 @ 6e0ea5d6:0327f353
2025-05-20 01:35:20
@ 6e0ea5d6:0327f353
2025-05-20 01:35:20**Ascolta bene! ** A man's sentimental longing, though often disguised in noble language and imagination, is a sickness—not a virtue.
It begins as a slight inclination toward tenderness, cloaked in sweetness. Then it reveals itself as a masked addiction: a constant need to be seen by a woman, validated by her, and reciprocated—as if someone else's affection were the only anchor preventing the shipwreck of his emotions.
The man who understands the weight of leadership seeks no applause, no gratitude, not even romantic love. He knows that his role is not theatrical but structural. He is not measured by the emotion he evokes, but by the stability he ensures. Being a true man is not ornamental. He is not a decorative symbol in the family frame.
We live in an era where male roles have been distorted by an overindulgence in emotion. The man stopped guiding and began asking for direction. His firmness was exchanged for softness, his decisiveness for hesitation. Trying to please, many have given up authority. Trying to love, they’ve begun to bow. A man who begs for validation within his own home is not a leader—he is a guest. And when the patriarch has to ask for a seat at the table he should preside over and sustain, something has already been irreversibly inverted.
Unexamined longing turns into pleading. And all begging is the antechamber of humiliation. A man who never learned to cultivate dignified solitude will inevitably fall to his knees in desperation. And then, he yields. Yields to mediocre presence, to shallow affection, to constant disrespect. He smiles while he bleeds, praises the one who despises him, accepts crumbs and pretends it’s a banquet. All of it, cazzo... just to avoid the horror of being alone.
Davvero, amico mio, for the men who beg for romance, only the consolation of being remembered will remain—not with respect, but with pity and disgust.
The modern world feeds the fragile with illusions, but reality spits them out. Sentimental longing is now celebrated as sensitivity. But every man who nurtures it as an excuse will, sooner or later, pay for it with his dignity.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ fd06f542:8d6d54cd
2025-05-20 01:18:45
@ fd06f542:8d6d54cd
2025-05-20 01:18:45🧱 NostrTrust Initial Trust Score List (V0.1)
This list defines the initial trust scores (T Score) for key members of the Nostr community based on their contributions, reputation, and role in the ecosystem. The goal is to seed a decentralized trust system that encourages quality interactions and authentic contributions.
> ⚠️ Note: This is an draft version.
✅ Initial T Score Allocation Rules
| User Type | Initial T Score Range | Criteria | |-----------|------------------------|----------| | Founder | 10,000 | Creator of the Nostr protocol | | Core Developers | 5,000 - 8,000 | Major contributors to core codebase, clients, or infrastructure | | Active Contributors | 1,000 - 4,000 | Recognized long-term contributors to content, tools, or community |
👤 Initial Trust Score Table
| Name / Alias | npub | Initial T Score | Justification | |--------------|------|------------------|----------------| | fiatjaf | npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 | 10,000 | Creator of the Nostr protocol | |Jack|npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m|9,000|| | jb55 | npub1xtscya34g58tk0z605fvr788k263gsu6cy9x0mhnm87echrgufzsevkk5s | 7,000 | Developer of tools, relays, and early Nostr integrations,made damus | |Alex Gleason | npub1q3sle0kvfsehgsuexttt3ugjd8xdklxfwwkh559wxckmzddywnws6cd26p | 7,000 || |PABLOF7z|npub1l2vyh47mk2p0qlsku7hg0vn29faehy9hy34ygaclpn66ukqp3afqutajft|7,000|NDK| |DASHU|npub19yeqjawls407xjnmgkk6yss7936pcd7qzd5srlj8wye6j8433vrsjazqwk|4,000|Nostrmo | |Moss|npub129z0az8lgffuvsywazww07hx75qas3veh3dazsq56z8y39v86khs2uy5gm|4,000| freerse.com| |w|npub10td4yrp6cl9kmjp9x5yd7r8pm96a5j07lk5mtj2kw39qf8frpt8qm9x2wl|4,000| 0xchat | |Cody Tseng|npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wl|4,000| jumble.social| |nostr_cn_dev|npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm|1,000|nostrbook.com,NostrTrust,nostrbridge| |hzrd149|npub1ye5ptcxfyyxl5vjvdjar2ua3f0hynkjzpx552mu5snj3qmx5pzjscpknpr|6,000|blossom,nostrudel| ||||| ||||| ||||| ||||| |||||
-
 @ 9be6a199:6e133301
2025-05-19 23:11:35
@ 9be6a199:6e133301
2025-05-19 23:11:35this is the content
this is an update
-
 @ 9be6a199:6e133301
2025-05-19 22:39:28
@ 9be6a199:6e133301
2025-05-19 22:39:28sdsdsd
-
 @ 8bad92c3:ca714aa5
2025-05-20 01:45:00
@ 8bad92c3:ca714aa5
2025-05-20 01:45:00Marty's Bent

Here's a great presentation from our good friend Michael Goldstein, President of The Nakamoto Institute titled Hodl for Good. He gave it earlier this year at the BitBlockBoom Conference, and I think it's something everyone reading this should take 25 minutes to watch. Especially if you find yourself wondering whether or not it's a good idea to spend bitcoin at any given point in time. Michael gives an incredible Austrian Economics 101 lesson on the importance of lowering one's time preference and fully understanding the importance of hodling bitcoin. For the uninitiated, it may seem that the hodl meme is nothing more than a call to hoard bitcoins in hopes of getting rich eventually. However, as Michael points out, there's layers to the hodl meme and the good that hodling can bring individuals and the economy overall.
The first thing one needs to do to better understand the hodl meme is to completely flip the framing that is typically thrust on bitcoiners who encourage others to hodl. Instead of ceding that hodling is a greedy or selfish action, remind people that hodling, or better known as saving, is the foundation of capital formation, from which all productive and efficient economic activity stems. Number go up technology is great and it really matters. It matters because it enables anybody leveraging that technology to accumulate capital that can then be allocated toward productive endeavors that bring value to the individual who creates them and the individual who buys them.
When one internalizes this, it enables them to turn to personal praxis and focus on minimizing present consumption while thinking of ways to maximize long-term value creation. Live below your means, stack sats, and use the time that you're buying to think about things that you want in the future. By lowering your time preference and saving in a harder money you will have the luxury of demanding higher quality goods in the future. Another way of saying this is that you will be able to reshape production by voting with your sats. Initially when you hold them off the market by saving them - signaling that the market doesn't have goods worthy of your sats - and ultimately by redeploying them into the market when you find higher quality goods that meet the standards desire.
The first part of this equation is extremely important because it sends a signal to producers that they need to increase the quality of their work. As more and more individuals decide to use bitcoin as their savings technology, the signal gets stronger. And over many cycles we should begin to see low quality cheap goods exit the market in favor of higher quality goods that provide more value and lasts longer and, therefore, make it easier for an individual to depart with their hard-earned and hard-saved sats. This is only but one aspect that Michael tries to imbue throughout his presentation.
The other is the ability to buy yourself leisure time when you lower your time preference and save more than you spend. When your savings hit a critical tipping point that gives you the luxury to sit back and experience true leisure, which Michael explains is not idleness, but the contemplative space to study, create art, refine taste, and to find what "better goods" actually are. Those who can experience true leisure while reaping the benefits of saving in a hard asset that is increasing in purchasing power significantly over the long term are those who build truly great things. Things that outlast those who build them. Great art, great monuments, great institutions were all built by men who were afforded the time to experience leisure. Partly because they were leveraging hard money as their savings and the place they stored the profits reaped from their entrepreneurial endeavors.
If you squint and look into the future a couple of decades, it isn't hard to see a reality like this manifesting. As more people begin to save in Bitcoin, the forces of supply and demand will continue to come into play. There will only ever be 21 million bitcoin, there are around 8 billion people on this planet, and as more of those 8 billion individuals decide that bitcoin is the best savings vehicle, the price of bitcoin will rise.
When the price of bitcoin rises, it makes all other goods cheaper in bitcoin terms and, again, expands the entrepreneurial opportunity. The best part about this feedback loop is that even non-holders of bitcoin benefit through higher real wages and faster tech diffusion. The individuals and business owners who decide to hodl bitcoin will bring these benefits to the world whether you decide to use bitcoin or not.
This is why it is virtuous to hodl bitcoin. The potential for good things to manifest throughout the world increase when more individuals decide to hodl bitcoin. And as Michael very eloquently points out, this does not mean that people will not spend their bitcoin. It simply means that they have standards for the things that they will spend their bitcoin on. And those standards are higher than most who are fully engrossed in the high velocity trash economy have today.
In my opinion, one of those higher causes worthy of a sats donation is The Nakamoto Institute. Consider donating so they can preserve and disseminate vital information about bitcoin and its foundations.
The Shell Game: How Health Narratives May Distract from Vaccine Risks
In our recent podcast, Dr. Jack Kruse presented a concerning theory about public health messaging. He argues that figures like Casey and Callie Means are promoting food and exercise narratives as a deliberate distraction from urgent vaccine issues. While no one disputes healthy eating matters, Dr. Kruse insists that focusing on "Froot Loops and Red Dye" diverts attention from what he sees as immediate dangers of mRNA vaccines, particularly for children.
"It's gonna take you 50 years to die from processed food. But the messenger jab can drop you like Damar Hamlin." - Dr Jack Kruse
Dr. Kruse emphasized that approximately 25,000 children per month are still receiving COVID vaccines despite concerns, with 3 million doses administered since Trump's election. This "shell game," as he describes it, allows vaccines to remain on childhood schedules while public attention fixates on less immediate health threats. As host, I believe this pattern deserves our heightened scrutiny given the potential stakes for our children's wellbeing.
Check out the full podcast here for more on Big Pharma's alleged bioweapons program, the "Time Bank Account" concept, and how Bitcoin principles apply to health sovereignty.
Headlines of the Day
Aussie Judge: Bitcoin is Money, Possibly CGT-Exempt - via X
JPMorgan to Let Clients Buy Bitcoin Without Direct Custody - via X
Get our new STACK SATS hat - via tftcmerch.io
Mubadala Acquires $408.5M Stake in BlackRock Bitcoin ETF - via X
Take the First Step Off the Exchange
Bitkey is an easy, secure way to move your Bitcoin into self-custody. With simple setup and built-in recovery, it’s the perfect starting point for getting your coins off centralized platforms and into cold storage—no complexity, no middlemen.
Take control. Start with Bitkey.
Use the promo code *“TFTC20”* during checkout for 20% off
Ten31, the largest bitcoin-focused investor, has deployed 158,469 sats | $150.00M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/invest.
Final thought...
I've been walking from my house around Town Lake in Austin in the mornings and taking calls on the walk. Big fan of a walking call.
Get this newsletter sent to your inbox daily: https://www.tftc.io/bitcoin-brief/
Subscribe to our YouTube channels and follow us on Nostr and X:
@media screen and (max-width: 480px) { .mobile-padding { padding: 10px 0 !important; } .social-container { width: 100% !important; max-width: 260px !important; } .social-icon { padding: 0 !important; } .social-icon img { height: 32px !important; width: 32px !important; } .icon-cell { padding: 0 4px !important; } } .mj-column-per-33-333333333333336 { width: 25% !important; max-width: 25%; } .moz-text-html .mj-column-per-33-333333333333336 { width: 25% !important; max-width: 25%; } /* Helps with rendering in various email clients */ body { margin: 0 !important; padding: 0 !important; -webkit-text-size-adjust: 100% !important; -ms-text-size-adjust: 100% !important; } img { -ms-interpolation-mode: bicubic; } /* Prevents Gmail from changing the text color in email threads */ .im { color: inherit !important; }
[ @ 2f29aa33:38ac6f13
2025-05-17 12:59:01
@ 2f29aa33:38ac6f13
2025-05-17 12:59:01The Myth and the Magic
Picture this: a group of investors, huddled around a glowing computer screen, nervously watching Bitcoin’s price. Suddenly, someone produces a stick-no ordinary stick, but a magical one. With a mischievous grin, they poke the Bitcoin. The price leaps upward. Cheers erupt. The legend of the Bitcoin stick is born.
But why does poking Bitcoin with a stick make the price go up? Why does it only work for a lucky few? And what does the data say about this mysterious phenomenon? Let’s dig in, laugh a little, and maybe learn the secret to market-moving magic.

The Statistical Side of Stick-Poking
Bitcoin’s Price: The Wild Ride
Bitcoin’s price is famous for its unpredictability. In the past year, it’s soared, dipped, and soared again, sometimes gaining more than 50% in just a few months. On a good day, billions of dollars flow through Bitcoin trades, and the price can jump thousands in a matter of hours. Clearly, something is making this happen-and it’s not just spreadsheets and financial news.
What Actually Moves the Price?
-
Scarcity: Only 21 million Bitcoins will ever exist. When more people want in, the price jumps.
-
Big News: Announcements, rumors, and meme-worthy moments can send the price flying.
-
FOMO: When people see Bitcoin rising, they rush to buy, pushing it even higher.
-
Liquidations: When traders betting against Bitcoin get squeezed, it triggers a chain reaction of buying.
But let’s be honest: none of this is as fun as poking Bitcoin with a stick.

The Magical Stick: Not Your Average Twig
Why Not Every Stick Works
You can’t just grab any old branch and expect Bitcoin to dance. The magical stick is a rare artifact, forged in the fires of internet memes and blessed by the spirit of Satoshi. Only a chosen few possess it-and when they poke, the market listens.
Signs You Have the Magical Stick
-
When you poke, Bitcoin’s price immediately jumps a few percent.
-
Your stick glows with meme energy and possibly sparkles with digital dust.
-
You have a knack for timing your poke right after a big event, like a halving or a celebrity tweet.
-
Your stick is rumored to have been whittled from the original blockchain itself.
Why Most Sticks Fail
-
No Meme Power: If your stick isn’t funny, Bitcoin ignores you.
-
Bad Timing: Poking during a bear market just annoys the blockchain.
-
Not Enough Hype: If the bitcoin community isn’t watching, your poke is just a poke.
-
Lack of Magic: Some sticks are just sticks. Sad, but true.

The Data: When the Stick Strikes
Let’s look at some numbers:
-
In the last month, Bitcoin’s price jumped over 20% right after a flurry of memes and stick-poking jokes.
-
Over the past year, every major price surge was accompanied by a wave of internet hype, stick memes, or wild speculation.
-
In the past five years, Bitcoin’s biggest leaps always seemed to follow some kind of magical event-whether a halving, a viral tweet, or a mysterious poke.
Coincidence? Maybe. But the pattern is clear: the stick works-at least when it’s magical.

The Role of Memes, Magic, and Mayhem
Bitcoin’s price is like a cat: unpredictable, easily startled, and sometimes it just wants to be left alone. But when the right meme pops up, or the right stick pokes at just the right time, the price can leap in ways that defy logic.
The bitcoin community knows this. That’s why, when Bitcoin’s stuck in a rut, you’ll see a flood of stick memes, GIFs, and magical thinking. Sometimes, it actually works.

The Secret’s in the Stick (and the Laughs)
So, does poking Bitcoin with a stick really make the price go up? If your stick is magical-blessed by memes, timed perfectly, and watched by millions-absolutely. The statistics show that hype, humor, and a little bit of luck can move markets as much as any financial report.
Next time you see Bitcoin stalling, don’t just sit there. Grab your stick, channel your inner meme wizard, and give it a poke. Who knows? You might just be the next legend in the world of bitcoin magic.
And if your stick doesn’t work, don’t worry. Sometimes, the real magic is in the laughter along the way.

-aco
@block height: 897,104
-
-
 @ 502ab02a:a2860397
2025-05-20 01:22:31
@ 502ab02a:a2860397
2025-05-20 01:22:31พอพูดถึงบริษัทอย่าง Formo ที่ทำชีสโดยไม่ใช้วัวเลย คนส่วนใหญ่จะนึกถึงคำว่า “นวัตกรรม” “ยั่งยืน” “ลดโลกร้อน” กันเป็นด่านแรก แต่พอเฮียมองทะลุม่านควันพวกนี้ไป จะเห็นทุนรายใหญ่ที่หนุนหลังอยู่ ซึ่งหลายเจ้าก็ไม่ใช่ผู้พิทักษ์โลก แต่เป็นผู้เล่นตัวจี๊ดในอุตสาหกรรมอาหารโลกมายาวนาน
หนึ่งในนั้นคือบริษัทจากเกาหลีใต้ชื่อ CJ CheilJedang ซึ่งอาจฟังดูไกลตัว แต่จริงๆ แล้ว เฮียว่าชื่อนี้โผล่ตามซองอาหารสำเร็จรูปในครัวคนไทยหลายบ้านโดยไม่รู้ตัว
ถ้าจะเข้าใจ Formo ให้ถึงแก่น เราต้องมองไปถึงทุนที่ “ใส่เงิน” และ “ใส่จุดยืน” ลงไปในบริษัทนั้น และหนึ่งในผู้ถือหุ้นรายสำคัญก็คือ CJ CheilJedang บริษัทเกาหลีใต้ที่ก่อตั้งมาตั้งแต่ปี 1953 โดยเริ่มจากการเป็นโรงงานผลิตน้ำตาล จากนั้นก็กินรวบแทบทุกวงจรอาหารของเกาหลี
โปรไฟล์ CJ แค่เห็นภาพรวมก็ขนลุกแล้วครับ ลูกพี่เราแข็งแกร่งขนาดไหน - เป็นเจ้าของแบรนด์ Bibigo ที่เราอาจจะคุ้นในสินค้า กิมจิ และ CJ Foods ที่มีขายทั่วโลก -เป็นผู้ผลิต กรดอะมิโน รายใหญ่ของโลก เช่น ไลซีน, ทรีโอนีน, ทริปโตแฟน ที่ใช้เป็นวัตถุดิบในอาหารสัตว์ แต่ตอนนี้หลายบริษัทเอาไปใส่ใน Plant-based food แล้วเคลมว่าเป็นโปรตีนสมบูรณ์ -เป็นเจ้าของโรงงานผลิต แบคทีเรียสายพันธุ์พิเศษ สำหรับการหมักหลายประเภท -ขึ้นชื่อเรื่อง bioscience โดยเฉพาะ precision fermentation ซึ่งเป็นเทคโนโลยีเดียวกับที่ Formo ใช้ผลิตเคซีน (โปรตีนในนมวัว)
แปลว่า CJ ไม่ได้มาลงทุนใน Formo แบบ “หวังผลกำไรเฉยๆ” แต่เขามองเห็น “อนาคตใหม่ของอาหาร” ที่ตัวเองจะเป็นเจ้าของต้นน้ำยันปลายน้ำ
คำถามก็คือเบื้องลึกการลงทุนใน Formo ใครได้อะไร? Formo ปิดรอบระดมทุน Series A ได้ประมาณ 50 ล้านดอลลาร์สหรัฐ เมื่อปี 2021 โดยมีนักลงทุนหลายเจ้า เช่น EQT Ventures, Elevat3 Capital, Atomico แต่ CJ CheilJedang ก็เป็นหนึ่งในผู้ลงทุนเชิงกลยุทธ์ (strategic investor) ที่เข้ามาแบบไม่ใช่แค่ลงเงิน แต่เอา เทคโนโลยี + เครือข่ายโรงงาน + ซัพพลายเชนระดับโลก มาเสริมให้ Formo ขยายได้เร็วขึ้น
การจับมือกันครั้งนี้มีนัยยะสำคัญครับ -Formo ได้ เทคโนโลยีหมักจุลินทรีย์ (ที่ CJ ถนัดมาก) และช่องทางกระจายสินค้าในเอเชีย -CJ ได้ ถือหุ้นในบริษัทที่กำลังจะเปลี่ยนภาพ “ผลิตภัณฑ์จากนม” ให้กลายเป็นสิ่งที่ไม่ต้องมีสัตว์อีกต่อไป ซึ่งจะเป็นกลยุทธ์สำคัญในการสร้างแบรนด์อาหารแห่งอนาคต ที่นมจะต้องมาจากโรงงานผลิตเท่านั้นจึงจะมีคุณสมบัติที่ดีทั้งสารอาหารและความสะอาด
CJ เองก็เคยประกาศต่อสื่อว่า อยากเป็น “Global Lifestyle Company” ซึ่งฟังดูเบาๆ แต่จริงๆ คือแผนใหญ่ในการ เปลี่ยนวิธีการกินของคนทั้งโลกได้เลยเช่นกัน -จาก “อาหารจริง” ไปเป็น “อาหารสังเคราะห์” (synthetic food) -จาก “ฟาร์มสัตว์” ไปเป็น “ถังหมักจุลินทรีย์” -จาก “ความหลากหลายตามธรรมชาติ” ไปเป็น “สูตรกลาง” ที่ควบคุมได้ในระดับโมเลกุล
การหนุนหลัง Formo จึงไม่ใช่เรื่องบังเอิญ แต่เป็นอีกหนึ่งหมากในกระดานใหญ่ที่ CJ วางไว้ เพื่อเป็นเจ้าของอาหารอนาคตแบบไม่ต้องเลี้ยงหมู ไก่ วัว แต่ครองเทคโนโลยีแทน
คำถามคือแล้วผู้บริโภคจะรู้ทันไหมว่า เบื้องหลังชีสที่ไม่มีวัว อาจมี “ทุนที่อยากครองโลกอาหาร” คำที่เคลมว่า “ยั่งยืน” อาจสร้างระบบอาหารใหม่ที่ยิ่งห่างจากธรรมชาติเข้าไปทุกที
คนที่เคย “กลัวสารเคมี” ในอาหารแปรรูป กลับกลืนผลิตภัณฑ์จากห้องแล็บ โดยคิดว่า “มันคือความสะอาดและอนาคต” #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ c296b5f7:c7282b53
2025-05-19 23:35:17
@ c296b5f7:c7282b53
2025-05-19 23:35:17testee
-
 @ c296b5f7:c7282b53
2025-05-19 23:18:42
@ c296b5f7:c7282b53
2025-05-19 23:18:42 -
 @ c296b5f7:c7282b53
2025-05-19 23:17:49
@ c296b5f7:c7282b53
2025-05-19 23:17:49https://curtlink.com/user/login powerdigital f1950610#@
-
 @ c296b5f7:c7282b53
2025-05-19 23:16:33
@ c296b5f7:c7282b53
2025-05-19 23:16:33enter in leaders group https://chat.whatsapp.com/EhI9fGsMbGPHd2cF5KQwC9
-
 @ 85fb39c4:81498307
2025-05-19 23:14:21
@ 85fb39c4:81498307
2025-05-19 23:14:21teste
-
 @ 85fb39c4:81498307
2025-05-19 23:07:11
@ 85fb39c4:81498307
2025-05-19 23:07:11It's my first post
-
 @ 4ba8e86d:89d32de4
2025-05-19 22:33:46
@ 4ba8e86d:89d32de4
2025-05-19 22:33:46O que é Cwtch? Cwtch (/kʊtʃ/ - uma palavra galesa que pode ser traduzida aproximadamente como “um abraço que cria um lugar seguro”) é um protocolo de mensagens multipartidário descentralizado, que preserva a privacidade, que pode ser usado para construir aplicativos resistentes a metadados.
Como posso pronunciar Cwtch? Como "kutch", para rimar com "butch".
Descentralizado e Aberto : Não existe “serviço Cwtch” ou “rede Cwtch”. Os participantes do Cwtch podem hospedar seus próprios espaços seguros ou emprestar sua infraestrutura para outras pessoas que buscam um espaço seguro. O protocolo Cwtch é aberto e qualquer pessoa é livre para criar bots, serviços e interfaces de usuário e integrar e interagir com o Cwtch.
Preservação de privacidade : toda a comunicação no Cwtch é criptografada de ponta a ponta e ocorre nos serviços cebola Tor v3.
Resistente a metadados : O Cwtch foi projetado de forma que nenhuma informação seja trocada ou disponibilizada a ninguém sem seu consentimento explícito, incluindo mensagens durante a transmissão e metadados de protocolo
Uma breve história do bate-papo resistente a metadados Nos últimos anos, a conscientização pública sobre a necessidade e os benefícios das soluções criptografadas de ponta a ponta aumentou com aplicativos como Signal , Whatsapp e Wire. que agora fornecem aos usuários comunicações seguras.
No entanto, essas ferramentas exigem vários níveis de exposição de metadados para funcionar, e muitos desses metadados podem ser usados para obter detalhes sobre como e por que uma pessoa está usando uma ferramenta para se comunicar.
Uma ferramenta que buscou reduzir metadados é o Ricochet lançado pela primeira vez em 2014. Ricochet usou os serviços cebola Tor v2 para fornecer comunicação criptografada segura de ponta a ponta e para proteger os metadados das comunicações.
Não havia servidores centralizados que auxiliassem no roteamento das conversas do Ricochet. Ninguém além das partes envolvidas em uma conversa poderia saber que tal conversa está ocorrendo.
Ricochet tinha limitações; não havia suporte para vários dispositivos, nem existe um mecanismo para suportar a comunicação em grupo ou para um usuário enviar mensagens enquanto um contato está offline.
Isto tornou a adoção do Ricochet uma proposta difícil; mesmo aqueles em ambientes que seriam melhor atendidos pela resistência aos metadados, sem saber que ela existe.
Além disso, qualquer solução para comunicação descentralizada e resistente a metadados enfrenta problemas fundamentais quando se trata de eficiência, privacidade e segurança de grupo conforme definido pelo consenso e consistência da transcrição.
Alternativas modernas ao Ricochet incluem Briar , Zbay e Ricochet Refresh - cada ferramenta procura otimizar para um conjunto diferente de compensações, por exemplo, Briar procura permitir que as pessoas se comuniquem mesmo quando a infraestrutura de rede subjacente está inoperante, ao mesmo tempo que fornece resistência à vigilância de metadados.
O projeto Cwtch começou em 2017 como um protocolo de extensão para Ricochet, fornecendo conversas em grupo por meio de servidores não confiáveis, com o objetivo de permitir aplicativos descentralizados e resistentes a metadados como listas compartilhadas e quadros de avisos.
Uma versão alfa do Cwtch foi lançada em fevereiro de 2019 e, desde então, a equipe do Cwtch dirigida pela OPEN PRIVACY RESEARCH SOCIETY conduziu pesquisa e desenvolvimento em cwtch e nos protocolos, bibliotecas e espaços de problemas subjacentes.
Modelo de Risco.
Sabe-se que os metadados de comunicações são explorados por vários adversários para minar a segurança dos sistemas, para rastrear vítimas e para realizar análises de redes sociais em grande escala para alimentar a vigilância em massa. As ferramentas resistentes a metadados estão em sua infância e faltam pesquisas sobre a construção e a experiência do usuário de tais ferramentas.
https://nostrcheck.me/media/public/nostrcheck.me_9475702740746681051707662826.webp
O Cwtch foi originalmente concebido como uma extensão do protocolo Ricochet resistente a metadados para suportar comunicações assíncronas de grupos multiponto por meio do uso de infraestrutura anônima, descartável e não confiável.
Desde então, o Cwtch evoluiu para um protocolo próprio. Esta seção descreverá os vários riscos conhecidos que o Cwtch tenta mitigar e será fortemente referenciado no restante do documento ao discutir os vários subcomponentes da Arquitetura Cwtch.
Modelo de ameaça.
É importante identificar e compreender que os metadados são omnipresentes nos protocolos de comunicação; é de facto necessário que tais protocolos funcionem de forma eficiente e em escala. No entanto, as informações que são úteis para facilitar peers e servidores também são altamente relevantes para adversários que desejam explorar tais informações.
Para a definição do nosso problema, assumiremos que o conteúdo de uma comunicação é criptografado de tal forma que um adversário é praticamente incapaz de quebrá-lo veja tapir e cwtch para detalhes sobre a criptografia que usamos, e como tal nos concentraremos em o contexto para os metadados de comunicação.
Procuramos proteger os seguintes contextos de comunicação:
• Quem está envolvido em uma comunicação? Pode ser possível identificar pessoas ou simplesmente identificadores de dispositivos ou redes. Por exemplo, “esta comunicação envolve Alice, uma jornalista, e Bob, um funcionário público”.
• Onde estão os participantes da conversa? Por exemplo, “durante esta comunicação, Alice estava na França e Bob estava no Canadá”.
• Quando ocorreu uma conversa? O momento e a duração da comunicação podem revelar muito sobre a natureza de uma chamada, por exemplo, “Bob, um funcionário público, conversou com Alice ao telefone por uma hora ontem à noite. Esta é a primeira vez que eles se comunicam.” *Como a conversa foi mediada? O fato de uma conversa ter ocorrido por meio de um e-mail criptografado ou não criptografado pode fornecer informações úteis. Por exemplo, “Alice enviou um e-mail criptografado para Bob ontem, enquanto eles normalmente enviam apenas e-mails de texto simples um para o outro”.
• Sobre o que é a conversa? Mesmo que o conteúdo da comunicação seja criptografado, às vezes é possível derivar um contexto provável de uma conversa sem saber exatamente o que é dito, por exemplo, “uma pessoa ligou para uma pizzaria na hora do jantar” ou “alguém ligou para um número conhecido de linha direta de suicídio na hora do jantar”. 3 horas da manhã."
Além das conversas individuais, também procuramos defender-nos contra ataques de correlação de contexto, através dos quais múltiplas conversas são analisadas para obter informações de nível superior:
• Relacionamentos: Descobrir relações sociais entre um par de entidades analisando a frequência e a duração de suas comunicações durante um período de tempo. Por exemplo, Carol e Eve ligam uma para a outra todos os dias durante várias horas seguidas.
• Cliques: Descobrir relações sociais entre um grupo de entidades que interagem entre si. Por exemplo, Alice, Bob e Eva se comunicam entre si.
• Grupos vagamente conectados e indivíduos-ponte: descobrir grupos que se comunicam entre si através de intermediários, analisando cadeias de comunicação (por exemplo, toda vez que Alice fala com Bob, ela fala com Carol quase imediatamente depois; Bob e Carol nunca se comunicam).
• Padrão de Vida: Descobrir quais comunicações são cíclicas e previsíveis. Por exemplo, Alice liga para Eve toda segunda-feira à noite por cerca de uma hora. Ataques Ativos
Ataques de deturpação.
O Cwtch não fornece registro global de nomes de exibição e, como tal, as pessoas que usam o Cwtch são mais vulneráveis a ataques baseados em declarações falsas, ou seja, pessoas que fingem ser outras pessoas:
O fluxo básico de um desses ataques é o seguinte, embora também existam outros fluxos:
•Alice tem um amigo chamado Bob e outro chamado Eve
• Eve descobre que Alice tem um amigo chamado Bob
• Eve cria milhares de novas contas para encontrar uma que tenha uma imagem/chave pública semelhante à de Bob (não será idêntica, mas pode enganar alguém por alguns minutos)
• Eve chama essa nova conta de "Eve New Account" e adiciona Alice como amiga.
• Eve então muda seu nome em "Eve New Account" para "Bob"
• Alice envia mensagens destinadas a "Bob" para a conta falsa de Bob de Eve Como os ataques de declarações falsas são inerentemente uma questão de confiança e verificação, a única maneira absoluta de evitá-los é os usuários validarem absolutamente a chave pública. Obviamente, isso não é o ideal e, em muitos casos, simplesmente não acontecerá .
Como tal, pretendemos fornecer algumas dicas de experiência do usuário na interface do usuário para orientar as pessoas na tomada de decisões sobre confiar em contas e/ou distinguir contas que possam estar tentando se representar como outros usuários.
Uma nota sobre ataques físicos A Cwtch não considera ataques que exijam acesso físico (ou equivalente) à máquina do usuário como praticamente defensáveis. No entanto, no interesse de uma boa engenharia de segurança, ao longo deste documento ainda nos referiremos a ataques ou condições que exigem tal privilégio e indicaremos onde quaisquer mitigações que implementámos falharão.
Um perfil Cwtch.
Os usuários podem criar um ou mais perfis Cwtch. Cada perfil gera um par de chaves ed25519 aleatório compatível com Tor.
Além do material criptográfico, um perfil também contém uma lista de Contatos (outras chaves públicas do perfil Cwtch + dados associados sobre esse perfil, como apelido e (opcionalmente) mensagens históricas), uma lista de Grupos (contendo o material criptográfico do grupo, além de outros dados associados, como apelido do grupo e mensagens históricas).
Conversões entre duas partes: ponto a ponto
https://nostrcheck.me/media/public/nostrcheck.me_2186338207587396891707662879.webp
Para que duas partes participem de uma conversa ponto a ponto, ambas devem estar on-line, mas apenas uma precisa estar acessível por meio do serviço Onion. Por uma questão de clareza, muitas vezes rotulamos uma parte como “ponto de entrada” (aquele que hospeda o serviço cebola) e a outra parte como “ponto de saída” (aquele que se conecta ao serviço cebola).
Após a conexão, ambas as partes adotam um protocolo de autenticação que:
• Afirma que cada parte tem acesso à chave privada associada à sua identidade pública.
• Gera uma chave de sessão efêmera usada para criptografar todas as comunicações futuras durante a sessão.
Esta troca (documentada com mais detalhes no protocolo de autenticação ) é negável offline , ou seja, é possível para qualquer parte falsificar transcrições desta troca de protocolo após o fato e, como tal - após o fato - é impossível provar definitivamente que a troca aconteceu de forma alguma.
Após o protocolo de autenticação, as duas partes podem trocar mensagens livremente.
Conversas em Grupo e Comunicação Ponto a Servidor
Ao iniciar uma conversa em grupo, é gerada uma chave aleatória para o grupo, conhecida como Group Key. Todas as comunicações do grupo são criptografadas usando esta chave. Além disso, o criador do grupo escolhe um servidor Cwtch para hospedar o grupo. Um convite é gerado, incluindo o Group Key, o servidor do grupo e a chave do grupo, para ser enviado aos potenciais membros.
Para enviar uma mensagem ao grupo, um perfil se conecta ao servidor do grupo e criptografa a mensagem usando a Group Key, gerando também uma assinatura sobre o Group ID, o servidor do grupo e a mensagem. Para receber mensagens do grupo, um perfil se conecta ao servidor e baixa as mensagens, tentando descriptografá-las usando a Group Key e verificando a assinatura.
Detalhamento do Ecossistema de Componentes
O Cwtch é composto por várias bibliotecas de componentes menores, cada uma desempenhando um papel específico. Algumas dessas bibliotecas incluem:
- abertoprivacidade/conectividade: Abstração de rede ACN, atualmente suportando apenas Tor.
- cwtch.im/tapir: Biblioteca para construção de aplicativos p2p em sistemas de comunicação anônimos.
- cwtch.im/cwtch: Biblioteca principal para implementação do protocolo/sistema Cwtch.
- cwtch.im/libcwtch-go: Fornece ligações C para Cwtch para uso em implementações de UI.
TAPIR: Uma Visão Detalhada
Projetado para substituir os antigos canais de ricochete baseados em protobuf, o Tapir fornece uma estrutura para a construção de aplicativos anônimos.
Está dividido em várias camadas:
• Identidade - Um par de chaves ed25519, necessário para estabelecer um serviço cebola Tor v3 e usado para manter uma identidade criptográfica consistente para um par.
• Conexões – O protocolo de rede bruto que conecta dois pares. Até agora, as conexões são definidas apenas através do Tor v3 Onion Services.
• Aplicativos - As diversas lógicas que permitem um determinado fluxo de informações em uma conexão. Os exemplos incluem transcrições criptográficas compartilhadas, autenticação, proteção contra spam e serviços baseados em tokens. Os aplicativos fornecem recursos que podem ser referenciados por outros aplicativos para determinar se um determinado peer tem a capacidade de usar um determinado aplicativo hospedado.
• Pilhas de aplicativos - Um mecanismo para conectar mais de um aplicativo, por exemplo, a autenticação depende de uma transcrição criptográfica compartilhada e o aplicativo peer cwtch principal é baseado no aplicativo de autenticação.
Identidade.
Um par de chaves ed25519, necessário para estabelecer um serviço cebola Tor v3 e usado para manter uma identidade criptográfica consistente para um peer.
InitializeIdentity - de um par de chaves conhecido e persistente:i,I
InitializeEphemeralIdentity - de um par de chaves aleatório: ie,Ie
Aplicativos de transcrição.
Inicializa uma transcrição criptográfica baseada em Merlin que pode ser usada como base de protocolos baseados em compromisso de nível superior
O aplicativo de transcrição entrará em pânico se um aplicativo tentar substituir uma transcrição existente por uma nova (aplicando a regra de que uma sessão é baseada em uma e apenas uma transcrição).
Merlin é uma construção de transcrição baseada em STROBE para provas de conhecimento zero. Ele automatiza a transformação Fiat-Shamir, para que, usando Merlin, protocolos não interativos possam ser implementados como se fossem interativos.
Isto é significativamente mais fácil e menos sujeito a erros do que realizar a transformação manualmente e, além disso, também fornece suporte natural para:
• protocolos multi-round com fases alternadas de commit e desafio;
• separação natural de domínios, garantindo que os desafios estejam vinculados às afirmações a serem provadas;
• enquadramento automático de mensagens, evitando codificação ambígua de dados de compromisso;
• e composição do protocolo, usando uma transcrição comum para vários protocolos.
Finalmente, o Merlin também fornece um gerador de números aleatórios baseado em transcrição como defesa profunda contra ataques de entropia ruim (como reutilização de nonce ou preconceito em muitas provas). Este RNG fornece aleatoriedade sintética derivada de toda a transcrição pública, bem como dos dados da testemunha do provador e uma entrada auxiliar de um RNG externo.
Conectividade Cwtch faz uso do Tor Onion Services (v3) para todas as comunicações entre nós.
Fornecemos o pacote openprivacy/connectivity para gerenciar o daemon Tor e configurar e desmontar serviços cebola através do Tor.
Criptografia e armazenamento de perfil.
Os perfis são armazenados localmente no disco e criptografados usando uma chave derivada de uma senha conhecida pelo usuário (via pbkdf2).
Observe que, uma vez criptografado e armazenado em disco, a única maneira de recuperar um perfil é recuperando a senha - como tal, não é possível fornecer uma lista completa de perfis aos quais um usuário pode ter acesso até inserir uma senha.
Perfis não criptografados e a senha padrão Para lidar com perfis "não criptografados" (ou seja, que não exigem senha para serem abertos), atualmente criamos um perfil com uma senha codificada de fato .
Isso não é o ideal, preferiríamos confiar no material de chave fornecido pelo sistema operacional, de modo que o perfil fosse vinculado a um dispositivo específico, mas esses recursos são atualmente uma colcha de retalhos - também notamos, ao criar um perfil não criptografado, pessoas que usam Cwtch estão explicitamente optando pelo risco de que alguém com acesso ao sistema de arquivos possa descriptografar seu perfil.
Vulnerabilidades Relacionadas a Imagens e Entrada de Dados
Imagens Maliciosas
O Cwtch enfrenta desafios na renderização de imagens, com o Flutter utilizando Skia, embora o código subjacente não seja totalmente seguro para a memória.
Realizamos testes de fuzzing nos componentes Cwtch e encontramos um bug de travamento causado por um arquivo GIF malformado, levando a falhas no kernel. Para mitigar isso, adotamos a política de sempre habilitar cacheWidth e/ou cacheHeight máximo para widgets de imagem.
Identificamos o risco de imagens maliciosas serem renderizadas de forma diferente em diferentes plataformas, como evidenciado por um bug no analisador PNG da Apple.
Riscos de Entrada de Dados
Um risco significativo é a interceptação de conteúdo ou metadados por meio de um Input Method Editor (IME) em dispositivos móveis. Mesmo aplicativos IME padrão podem expor dados por meio de sincronização na nuvem, tradução online ou dicionários pessoais.
Implementamos medidas de mitigação, como enableIMEPersonalizedLearning: false no Cwtch 1.2, mas a solução completa requer ações em nível de sistema operacional e é um desafio contínuo para a segurança móvel.
Servidor Cwtch.
O objetivo do protocolo Cwtch é permitir a comunicação em grupo através de infraestrutura não confiável .
Ao contrário dos esquemas baseados em retransmissão, onde os grupos atribuem um líder, um conjunto de líderes ou um servidor confiável de terceiros para garantir que cada membro do grupo possa enviar e receber mensagens em tempo hábil (mesmo que os membros estejam offline) - infraestrutura não confiável tem o objetivo de realizar essas propriedades sem a suposição de confiança.
O artigo original do Cwtch definia um conjunto de propriedades que se esperava que os servidores Cwtch fornecessem:
• O Cwtch Server pode ser usado por vários grupos ou apenas um.
• Um servidor Cwtch, sem a colaboração de um membro do grupo, nunca deve aprender a identidade dos participantes de um grupo.
• Um servidor Cwtch nunca deve aprender o conteúdo de qualquer comunicação.
• Um servidor Cwtch nunca deve ser capaz de distinguir mensagens como pertencentes a um grupo específico. Observamos aqui que essas propriedades são um superconjunto dos objetivos de design das estruturas de Recuperação de Informações Privadas.
Melhorias na Eficiência e Segurança
Eficiência do Protocolo
Atualmente, apenas um protocolo conhecido, o PIR ingênuo, atende às propriedades desejadas para garantir a privacidade na comunicação do grupo Cwtch. Este método tem um impacto direto na eficiência da largura de banda, especialmente para usuários em dispositivos móveis. Em resposta a isso, estamos ativamente desenvolvendo novos protocolos que permitem negociar garantias de privacidade e eficiência de maneiras diversas.
Os servidores, no momento desta escrita, permitem o download completo de todas as mensagens armazenadas, bem como uma solicitação para baixar mensagens específicas a partir de uma determinada mensagem. Quando os pares ingressam em um grupo em um novo servidor, eles baixam todas as mensagens do servidor inicialmente e, posteriormente, apenas as mensagens novas.
Mitigação de Análise de Metadados
Essa abordagem permite uma análise moderada de metadados, pois o servidor pode enviar novas mensagens para cada perfil suspeito exclusivo e usar essas assinaturas de mensagens exclusivas para rastrear sessões ao longo do tempo. Essa preocupação é mitigada por dois fatores:
- Os perfis podem atualizar suas conexões a qualquer momento, resultando em uma nova sessão do servidor.
- Os perfis podem ser "ressincronizados" de um servidor a qualquer momento, resultando em uma nova chamada para baixar todas as mensagens. Isso é comumente usado para buscar mensagens antigas de um grupo.
Embora essas medidas imponham limites ao que o servidor pode inferir, ainda não podemos garantir resistência total aos metadados. Para soluções futuras para esse problema, consulte Niwl.
Proteção contra Pares Maliciosos
Os servidores enfrentam o risco de spam gerado por pares, representando uma ameaça significativa à eficácia do sistema Cwtch. Embora tenhamos implementado um mecanismo de proteção contra spam no protótipo do Cwtch, exigindo que os pares realizem alguma prova de trabalho especificada pelo servidor, reconhecemos que essa não é uma solução robusta na presença de um adversário determinado com recursos significativos.
Pacotes de Chaves
Os servidores Cwtch se identificam por meio de pacotes de chaves assinados, contendo uma lista de chaves necessárias para garantir a segurança e resistência aos metadados na comunicação do grupo Cwtch. Esses pacotes de chaves geralmente incluem três chaves: uma chave pública do serviço Tor v3 Onion para o Token Board, uma chave pública do Tor v3 Onion Service para o Token Service e uma chave pública do Privacy Pass.
Para verificar os pacotes de chaves, os perfis que os importam do servidor utilizam o algoritmo trust-on-first-use (TOFU), verificando a assinatura anexada e a existência de todos os tipos de chave. Se o perfil já tiver importado o pacote de chaves do servidor anteriormente, todas as chaves são consideradas iguais.
Configuração prévia do aplicativo para ativar o Relé do Cwtch.
No Android, a hospedagem de servidor não está habilitada, pois essa opção não está disponível devido às limitações dos dispositivos Android. Essa funcionalidade está reservada apenas para servidores hospedados em desktops.
No Android, a única forma direta de importar uma chave de servidor é através do grupo de teste Cwtch, garantindo assim acesso ao servidor Cwtch.
Primeiro passo é Habilitar a opção de grupo no Cwtch que está em fase de testes. Clique na opção no canto superior direito da tela de configuração e pressione o botão para acessar as configurações do Cwtch.
Você pode alterar o idioma para Português do Brasil.Depois, role para baixo e selecione a opção para ativar os experimentos. Em seguida, ative a opção para habilitar o chat em grupo e a pré-visualização de imagens e fotos de perfil, permitindo que você troque sua foto de perfil.
https://pomf2.lain.la/f/eprhj0u3.mp4
Próximo passo é Criar um perfil.
Pressione o + botão de ação no canto inferior direito e selecione "Novo perfil" ou aberta no botão + adicionar novo perfil.
-
Selecione um nome de exibição
-
Selecione se deseja proteger
este perfil e salvo localmente com criptografia forte: Senha: sua conta está protegida de outras pessoas que possam usar este dispositivo
Sem senha: qualquer pessoa que tenha acesso a este dispositivo poderá acessar este perfil.
Preencha sua senha e digite-a novamente
Os perfis são armazenados localmente no disco e criptografados usando uma chave derivada de uma senha conhecida pelo usuário (via pbkdf2).
Observe que, uma vez criptografado e armazenado em disco, a única maneira de recuperar um perfil é recuperando a chave da senha - como tal, não é possível fornecer uma lista completa de perfis aos quais um usuário pode ter acesso até inserir um senha.
https://pomf2.lain.la/f/7p6jfr9r.mp4
O próximo passo é adicionar o FuzzBot, que é um bot de testes e de desenvolvimento.
Contato do FuzzBot: 4y2hxlxqzautabituedksnh2ulcgm2coqbure6wvfpg4gi2ci25ta5ad.
Ao enviar o comando "testgroup-invite" para o FuzzBot, você receberá um convite para entrar no Grupo Cwtch Test. Ao ingressar no grupo, você será automaticamente conectado ao servidor Cwtch. Você pode optar por sair do grupo a qualquer momento ou ficar para conversar e tirar dúvidas sobre o aplicativo e outros assuntos. Depois, você pode configurar seu próprio servidor Cwtch, o que é altamente recomendável. https://pomf2.lain.la/f/x4pm8hm8.mp4
Agora você pode utilizar o aplicativo normalmente. Algumas observações que notei: se houver demora na conexão com outra pessoa, ambas devem estar online. Se ainda assim a conexão não for estabelecida, basta clicar no ícone de reset do Tor para restabelecer a conexão com a outra pessoa.
Uma introdução aos perfis Cwtch.
Com Cwtch você pode criar um ou mais perfis . Cada perfil gera um par de chaves ed25519 aleatório compatível com a Rede Tor.
Este é o identificador que você pode fornecer às pessoas e que elas podem usar para entrar em contato com você via Cwtch.
Cwtch permite criar e gerenciar vários perfis separados. Cada perfil está associado a um par de chaves diferente que inicia um serviço cebola diferente.
Gerenciar Na inicialização, o Cwtch abrirá a tela Gerenciar Perfis. Nessa tela você pode:
- Crie um novo perfil.
- Desbloquear perfis.
- Criptografados existentes.
- Gerenciar perfis carregados.
- Alterando o nome de exibição de um perfil.
- Alterando a senha de um perfil Excluindo um perfil.
- Alterando uma imagem de perfil.
Backup ou exportação de um perfil.
Na tela de gerenciamento de perfil:
-
Selecione o lápis ao lado do perfil que você deseja editar
-
Role para baixo até a parte inferior da tela.
-
Selecione "Exportar perfil"
-
Escolha um local e um nome de arquivo.
5.confirme.
Uma vez confirmado, o Cwtch colocará uma cópia do perfil no local indicado. Este arquivo é criptografado no mesmo nível do perfil.
Este arquivo pode ser importado para outra instância do Cwtch em qualquer dispositivo.
Importando um perfil.
-
Pressione o +botão de ação no canto inferior direito e selecione "Importar perfil"
-
Selecione um arquivo de perfil Cwtch exportado para importar
-
Digite a senha associada ao perfil e confirme.
Uma vez confirmado, o Cwtch tentará descriptografar o arquivo fornecido usando uma chave derivada da senha fornecida. Se for bem-sucedido, o perfil aparecerá na tela Gerenciamento de perfil e estará pronto para uso.
OBSERVAÇÃO Embora um perfil possa ser importado para vários dispositivos, atualmente apenas uma versão de um perfil pode ser usada em todos os dispositivos ao mesmo tempo. As tentativas de usar o mesmo perfil em vários dispositivos podem resultar em problemas de disponibilidade e falhas de mensagens.
Qual é a diferença entre uma conexão ponto a ponto e um grupo cwtch?
As conexões ponto a ponto Cwtch permitem que 2 pessoas troquem mensagens diretamente. As conexões ponto a ponto nos bastidores usam serviços cebola Tor v3 para fornecer uma conexão criptografada e resistente a metadados. Devido a esta conexão direta, ambas as partes precisam estar online ao mesmo tempo para trocar mensagens.
Os Grupos Cwtch permitem que várias partes participem de uma única conversa usando um servidor não confiável (que pode ser fornecido por terceiros ou auto-hospedado). Os operadores de servidores não conseguem saber quantas pessoas estão em um grupo ou o que está sendo discutido. Se vários grupos estiverem hospedados em um único servidor, o servidor não conseguirá saber quais mensagens pertencem a qual grupo sem a conivência de um membro do grupo. Ao contrário das conversas entre pares, as conversas em grupo podem ser conduzidas de forma assíncrona, para que todos num grupo não precisem estar online ao mesmo tempo.
Por que os grupos cwtch são experimentais? Mensagens em grupo resistentes a metadados ainda são um problema em aberto . Embora a versão que fornecemos no Cwtch Beta seja projetada para ser segura e com metadados privados, ela é bastante ineficiente e pode ser mal utilizada. Como tal, aconselhamos cautela ao usá-lo e apenas o fornecemos como um recurso opcional.
Como posso executar meu próprio servidor Cwtch? A implementação de referência para um servidor Cwtch é de código aberto . Qualquer pessoa pode executar um servidor Cwtch, e qualquer pessoa com uma cópia do pacote de chaves públicas do servidor pode hospedar grupos nesse servidor sem que o operador tenha acesso aos metadados relacionados ao grupo .
https://git.openprivacy.ca/cwtch.im/server
https://docs.openprivacy.ca/cwtch-security-handbook/server.html
Como posso desligar o Cwtch? O painel frontal do aplicativo possui um ícone do botão "Shutdown Cwtch" (com um 'X'). Pressionar este botão irá acionar uma caixa de diálogo e, na confirmação, o Cwtch será desligado e todos os perfis serão descarregados.
Suas doações podem fazer a diferença no projeto Cwtch? O Cwtch é um projeto dedicado a construir aplicativos que preservam a privacidade, oferecendo comunicação de grupo resistente a metadados. Além disso, o projeto também desenvolve o Cofre, formulários da web criptografados para ajudar mútua segura. Suas contribuições apoiam iniciativas importantes, como a divulgação de violações de dados médicos em Vancouver e pesquisas sobre a segurança do voto eletrônico na Suíça. Ao doar, você está ajudando a fechar o ciclo, trabalhando com comunidades marginalizadas para identificar e corrigir lacunas de privacidade. Além disso, o projeto trabalha em soluções inovadoras, como a quebra de segredos através da criptografia de limite para proteger sua privacidade durante passagens de fronteira. E também tem a infraestrutura: toda nossa infraestrutura é open source e sem fins lucrativos. Conheça também o Fuzzytags, uma estrutura criptográfica probabilística para marcação resistente a metadados. Sua doação é crucial para continuar o trabalho em prol da privacidade e segurança online. Contribua agora com sua doação
https://openprivacy.ca/donate/
onde você pode fazer sua doação em bitcoin e outras moedas, e saiba mais sobre os projetos. https://openprivacy.ca/work/
Link sobre Cwtch
https://cwtch.im/
https://git.openprivacy.ca/cwtch.im/cwtch
https://docs.cwtch.im/docs/intro
https://docs.openprivacy.ca/cwtch-security-handbook/
Baixar #CwtchDev
cwtch.im/download/
https://play.google.com/store/apps/details?id=im.cwtch.flwtch
-
 @ 7953d1fa:69c8039d
2025-05-20 02:39:56
@ 7953d1fa:69c8039d
2025-05-20 02:39:56No mundo digital em constante evolução, plataformas de entretenimento online vêm ganhando espaço entre os brasileiros que buscam diversão, emoção e recompensas. Uma das opções que tem se destacado recentemente é a KK999, uma plataforma moderna, segura e repleta de oportunidades para jogadores de todos os níveis. Com uma ampla gama de jogos envolventes e uma experiência de usuário otimizada, o KK999 está conquistando cada vez mais adeptos no Brasil.
Introdução à Plataforma KK999 O KK999 se diferencia por oferecer uma experiência completa e intuitiva desde o primeiro acesso. A interface da plataforma foi cuidadosamente projetada para ser amigável, permitindo que novos usuários se cadastrem rapidamente e naveguem com facilidade. Tudo é pensado para garantir que o jogador tenha uma experiência fluida, sem complicações e com total transparência.
Além disso, o kk999se destaca por sua forte infraestrutura de segurança. Utilizando tecnologia de criptografia de ponta, os dados dos usuários são protegidos em todas as transações, garantindo tranquilidade para quem deseja apenas se divertir. Outro ponto importante é o suporte ao cliente, que está disponível 24 horas por dia, com atendimento em português, pronto para auxiliar com qualquer dúvida ou necessidade.
Variedade de Jogos para Todos os Gostos Um dos grandes atrativos do KK999 é a impressionante variedade de jogos disponíveis. Desde os tradicionais jogos de cartas até opções modernas com gráficos avançados, a plataforma atende todos os estilos de jogadores. Entre os destaques, estão as famosas roletas virtuais, jogos de pesca interativa, slot machines com temas variados e jogos ao vivo que simulam a sensação de estar em uma sala de jogos física.
Os slots, por exemplo, são um sucesso entre os brasileiros, oferecendo desde títulos clássicos com frutas e números até aventuras temáticas com bônus emocionantes. Os jogos de cartas também têm grande popularidade, incluindo versões modernas de pôquer, bacará e outros jogos estratégicos que desafiam a mente do jogador.
Para quem gosta de competir em tempo real, o KK999 oferece jogos ao vivo com crupiês reais e interatividade instantânea, proporcionando uma experiência imersiva e cheia de adrenalina. Tudo isso com transmissões de alta qualidade e conexão estável.
Experiência do Jogador: Diversão e Confiabilidade A experiência do jogador é uma das maiores prioridades do KK999. Desde o primeiro cadastro até as jogadas mais avançadas, a plataforma investe em funcionalidades que aumentam o conforto e a confiança do usuário. A navegação é rápida, os jogos carregam com eficiência e as recompensas são distribuídas com agilidade.
Outro fator que atrai muitos jogadores é o sistema de bônus e promoções. O KK999 frequentemente disponibiliza ofertas especiais para novos membros e prêmios para usuários frequentes, incentivando a fidelidade e aumentando ainda mais as chances de ganhar.
Além disso, o KK999 oferece uma experiência totalmente otimizada para dispositivos móveis. Seja no celular ou tablet, o jogador pode acessar todos os recursos da plataforma de qualquer lugar, a qualquer momento, sem perder desempenho ou qualidade.
Conclusão O KK999 se consolida como uma das principais plataformas de entretenimento digital no Brasil, reunindo inovação, segurança e uma variedade impressionante de jogos. Ideal tanto para iniciantes quanto para jogadores experientes, o site oferece tudo o que é necessário para transformar momentos comuns em experiências emocionantes.
-
 @ 7953d1fa:69c8039d
2025-05-20 02:39:23
@ 7953d1fa:69c8039d
2025-05-20 02:39:23O cenário do entretenimento online no Brasil vem evoluindo rapidamente, e uma das plataformas que mais se destaca atualmente é a 8CC. Com uma proposta moderna, intuitiva e voltada para a melhor experiência do usuário, a 8CC conquistou a confiança de milhares de jogadores que buscam diversão, praticidade e oportunidades de ganhos reais em um ambiente seguro.
Conhecendo a Plataforma 8CC A 8CC é uma plataforma digital desenvolvida para atender tanto iniciantes quanto jogadores experientes. Sua interface amigável e bem organizada facilita a navegação mesmo para quem nunca teve contato com esse tipo de entretenimento antes. Compatível com computadores, tablets e celulares, o site é totalmente responsivo, o que significa que você pode se divertir de qualquer lugar, a qualquer hora.
Um dos diferenciais da 8cc é o seu compromisso com a segurança dos usuários. A plataforma utiliza tecnologia de criptografia de ponta para garantir a proteção de dados pessoais e transações financeiras. Além disso, o suporte ao cliente está sempre disponível para tirar dúvidas, resolver problemas e oferecer o melhor atendimento possível.
Diversidade de Jogos para Todos os Gostos Na 8CC, os jogadores têm acesso a uma vasta seleção de jogos online, desenvolvidos pelos principais provedores do mercado internacional. Isso garante alta qualidade gráfica, mecânicas inovadoras e excelente desempenho.
Entre os jogos mais populares da plataforma estão:
Slots (caça-níqueis): com temas variados, rodadas bônus e jackpots progressivos que proporcionam grandes emoções.
Jogos de mesa clássicos: como roleta, blackjack e bacará, com versões que imitam perfeitamente a experiência de jogo ao vivo.
Jogos com crupiês em tempo real: transmitidos com qualidade HD, esses jogos trazem interatividade e realismo, permitindo que o jogador se sinta dentro de um ambiente físico de alto padrão.
A plataforma também disponibiliza jogos de habilidade e apostas esportivas ao vivo, oferecendo uma experiência ainda mais completa e personalizada de acordo com o perfil de cada usuário.
Experiência do Jogador na 8CC Quem já experimentou jogar na 8CC sabe o quanto a plataforma valoriza o conforto e a satisfação de seus usuários. Desde o momento do cadastro até o resgate de ganhos, tudo é feito de forma simples, rápida e segura. O processo de registro é intuitivo, exigindo apenas alguns dados básicos, e os métodos de pagamento são variados, aceitando transferências bancárias, carteiras digitais e até criptomoedas.
Outro destaque é o sistema de recompensas e promoções. A 8CC frequentemente oferece bônus de boas-vindas, rodadas grátis e campanhas especiais para usuários fiéis, o que aumenta ainda mais as chances de ganhar e prolonga a diversão. Além disso, a plataforma promove torneios e desafios semanais com prêmios atrativos, incentivando a competição saudável entre os jogadores.
Por Que Escolher a 8CC? Existem muitas razões para escolher a 8CC como sua principal plataforma de jogos online:
Confiabilidade e segurança em todas as operações;
Variedade de jogos para todos os perfis;
Interface moderna e de fácil navegação;
Promoções e bônus frequentes;
Atendimento ao cliente eficiente e disponível 24 horas.
Se você busca uma experiência diferenciada, com diversão garantida e a possibilidade de transformar seu tempo livre em momentos empolgantes, a 8CC é a escolha certa. Descubra agora mesmo tudo o que essa plataforma inovadora tem a oferecer e junte-se à comunidade que está revolucionando o entretenimento digital no Brasil.
-
 @ 6b0a60cf:b952e7d4
2025-05-19 22:33:33
@ 6b0a60cf:b952e7d4
2025-05-19 22:33:33タイトルは釣りです。そんなこと微塵も思っていません。 本稿はアウトボックスモデルの実装に関してうだうだ考えるコーナーです。 ダムスに関して何か言いたいわけではないので先にタイトル回収しておきます。
- NIP-65を守る気なんかさらさら無いのにNIP-65に書いてあるkind:10002のReadリレーの意味を知っていながら全然違う使い方をしているのは一部の和製クライアントの方だよね
- NIP-65を守る気が無いならkind:10002を使うべきではなく、独自仕様でリレーを保存するべきだよね
- アウトボックスモデルを採用しているクライアントからすれば仕様と異なる実装をしてしまっているクライアントが迷惑だと思われても仕方ないよね
- と考えればダムスの方が潔いよね
- とはいえkind:3のcontentは空にしろって言われてんだからやっぱダムスはゴミだわ
- やるとしたらRabbitみたいにローカルに保存するか、別デバイス間で同期したいならkind:30078を使うべきだよね
アウトボックスモデルはなぜ人気がないのか
言ってることはとてもいいと思うんですよ。 欠点があるとすれば、
- 末端のユーザーからすればreadリレーとwriteリレーと書かれると直感的にイメージされるものとかけ離れている
- 正しく設定してもらうには相当の説明が必要
- フォローTLを表示しようとすれば非常にたくさんのリレーと接続することになり現実的ではない
- なるほど完璧な作戦っスねーっ 不可能だという点に目をつぶればよぉ~
余談ですが昔irisでログインした時に localhost のリレーに繋ごうとしてiris壊れたって思ったけど今思えばアウトボックスモデルを忠実に実装してたんじゃないかな…。
現実的に実装する方法は無いのか
これでReadすべきリレーをシミュレーションできる。 https://nikolat.github.io/nostr-relay-trend/ フォローイーのWriteリレーを全部購読しようとすると100個近いリレー数になるので現実的ではありません。 しかしフォローイーのWriteリレーのうち1個だけでよい、とする条件を仮に追加すると一気にハードルが下がります。私の場合はReadリレー含めて7個のリレーに収まりました。 Nos Haikuはとりあえずこの方針でいくことにしました。
今後どうしていきたいのか
エンドユーザーとしての自分の志向としては、自分が指定したリレーだけを購読してほしい、勝手に余計なリレーを読みに行かないでほしい、という気持ちがあり、現状の和製クライアントの仕様を気に入っています。 仮にNos Haikuでアウトボックスモデルを採用しつつ自分の決めたリレーに接続するハイブリッド実装を考えるとすれば、
あなたの購読するリレーはこれですよー - Read(inbox) Relays (あなたへのメンションが届くリレー) - wss://relay1.example.com/ - wss://relay2.example.com/ - wss://relay3.example.com/ - Followee's Write Relays (フォローイーが書き込んでいるリレー) - wss://relay4.example.com/ - wss://relay5.example.com/ - wss://relay6.example.com/って出して、チェックボックス付けてON/OFFできるようにして最終的に購読するリレーをユーザーに決めてもらう感じかな……って漠然と考えています。よほど時間を持て余したときがあればやってみるかも。
あとリレーを数は仕方ないとしてリレーごとにフォローイーの投稿だけを取得するようにした方が理にかなってるよね。全部のリレーから全部のフォローイーの投稿を取得しようとしたら(実装はシンプルで楽だけど)通信量が大変だよね。 rx-nostr の Forward Strategy ってリレーごとにREQかえて一度に購読できるっけ?
常にひとつ以下の REQ サブスクリプションを保持します。
って書いてあるから無理なのかな? あとReadリレーは純粋に自分へのメンション(pタグ付き)イベントのみを購読するようにした方がいい気がする。スパム対策としてかなり有効だと思うので。スパムはNIP-65に準拠したりはしていないでしょうし。 まぁ、NIP-65に準拠していないクライアントからのメンションは届かなくなってしまうわけですが。
-
 @ cae03c48:2a7d6671
2025-05-19 22:21:46
@ cae03c48:2a7d6671
2025-05-19 22:21:46Bitcoin Magazine

BitMine Launches Bitcoin Treasury Advisory Practice, Secures $4M Deal with First ClientToday, BitMine Immersion Technologies, Inc. (OTCQX: BMNRD) announced the launch of its Bitcoin Treasury Advisory Practice and a $4 million deal with a U.S. exchange-listed company. The deal saw Bitmine surpass its last year’s total revenue in that single transaction alone, according to the announcement.
BitMine ( OTCQX: $BMNRD $BMNR) launches Bitcoin Treasury Advisory Practice and secures $4M deal with first client.
This single transaction exceeds our 2024 revenue and sets the stage for major growth.
Read now: https://t.co/R89K3WXdZZ pic.twitter.com/5vIvlYPZUY
— Bitmine Immersion Technologies, Inc. (@BitMNR) May 19, 2025
BitMine will provide “Mining as a Service” (MaaS) by leasing 3,000 Bitcoin ASIC miners to the client through December 30, 2025, in a $3.2 million lease deal, with $1.6 million paid upfront. Additionally, the client has signed an $800,000 consulting agreement for one year focusing on Bitcoin Mining-as-a-Service and Bitcoin Treasury Strategy.
“Currently, there are almost 100 public companies that have adopted Bitcoin as a treasury holding. We expect this number to grow in the future. As more companies adopt Bitcoin treasury strategies, the need for infrastructure, revenue generation, and expert guidance grows along with it,” said Jonathan Bates, CEO of BitMine. “This single transaction is greater than our entire 2024 fiscal year revenue, and we feel there is an opportunity to acquire more clients in the near future as interest in Bitcoin ownership grows.”
BitMine’s first quarter 2025 results showed strong revenue growth, with GAAP revenue rising approximately 135% to $1.2 million, up from $511,000 in Q1 2024, supported by an expanded mining capacity of 4,640 miners as of November 30, 2024, compared to 1,606 the previous year. Despite this growth, the company reported a net loss of $3.9 million in Q1 2025, primarily due to a one-time, non-cash accounting adjustment related to preferred stock; excluding this charge, the adjusted loss was approximately $975,000, consistent with the prior year’s results.
$BMNR reports a 135% revenue increase YOY for Q1 2025 and tripled self-mining capacity with 3,000 new miners! CEO Jonathan Bates credits a team-driven approach and creative financing for this growth.
Read the full release here: https://t.co/slNrZv8Ocn pic.twitter.com/Gb4tk1UfAO— Bitmine Immersion Technologies, Inc. (@BitMNR) January 13, 2025
BitMine’s new Bitcoin Treasury Advisory Practice, along with the $4 million deal, joins a trend among public companies exploring Bitcoin not just as a treasury asset but also as a source of revenue.
This post BitMine Launches Bitcoin Treasury Advisory Practice, Secures $4M Deal with First Client first appeared on Bitcoin Magazine and is written by Oscar Zarraga Perez.
-
 @ bf47c19e:c3d2573b
2025-05-19 21:41:37
@ bf47c19e:c3d2573b
2025-05-19 21:41:37Originalni tekst na bitcoin-balkan.com.
Pregled sadržaja
- Šta je Bitcoin?
- Šta Bitcoin može da učini za vas?
- Zašto ljudi kupuju Bitcoin?
- Da li je vaš novac siguran u dolarima, kućama, akcijama ili zlatu?
- Šta je bolje za štednju od dolara, kuća i akcija?
- Po čemu se Bitcoin razlikuje od ostalih valuta?
- kako Bitcoin spašava svet?
- Kako mogu da saznam više o Bitcoin-u?
Bitcoin čini da štednja novca bude kul – i praktična – ponovo. Ovaj članak objašnjava kako i zašto.
Šta je Bitcoin?
Bitcoin se naziva digitalno zlato, mašina za istinu, blockchain, peer to peer mreža čvorova, energetski ponor i još mnogo toga. Bitcoin je, u stvari, sve ovo. Međutim, ova objašnjenja su često toliko tehnička i suvoparna, da bi većina ljudi radije gledala kako trava raste. Što je najvažnije, ova objašnjenja ne pokazuju kako Bitcoin ima bilo kakve koristi za vas.
iPod nije postao kulturološka senzacija jer ga je Apple nazvao „prenosnim digitalnim medijskim uređajem“. Postao je senzacija jer su ga zvali “1,000 pesama u vašem džepu.”
Ne zanima vas šta je Bitcoin. Vas zanima šta on može da učini za vas.
Baš kao i Internet, vaš auto, vaš telefon, kao i mnogi drugi uređaji i sistemi koje svakodnevno koristite, vi ne treba da znate šta je Bitcoin ili kako to funkcioniše da biste razumeli šta on može da učini za vas.
Šta Bitcoin može da učini za vas?
Bitcoin može da sačuva vaš teško zarađeni novac.
Bitcoin je stekao veliku pažnju u 2017. i 2018. godini zbog svoje spekulativne upotrebe. Mnogi ljudi su ga kupili nadajući se da će se obogatiti. Cena je naglo porasla, a zatim se srušila. Ovo nije bio prvi put da je Bitcoin uradio to. Međutim, niko nikada nije izgubio novac držeći bitcoin duže od 3,5 godine – ćak i ako je kupio na apsolutnim vrhovima.
Zašto Bitcoin konstantno raste? Ljudi počinju da shvataju koliko je Bitcoin moćan, kao način uštede novca u svetu u kojem je ’novac’ poput dolara, eura i drugih nacionalnih valuta dizajniran da gubi vrednost.
Ovo čini Bitcoin odličnom opcijom za štednju novca na nekoliko godina ili više. Bitcoin je bolji od štednje novca u dolarima, akcijama, nekretninama, pa čak i u zlatu.
Zato pokušajte da zaboravite na trenutak na razumevanje blockchaina, digitalne valute, kriptografije, seed fraza, novčanika, rudarstva i svih ostalih nerazumljivih termina. Za sada, razgovarajmo o tome zašto ljudi kupuju Bitcoin: razlog je prostiji nego što vi mislite.
Zašto ljudi kupuju Bitcoin?
Naravno, svako ima svoj razlog za kupovinu Bitcoin-a. Jedan od razloga, koji verovatno često čujete, je taj što mu vrednost raste. Ljudi žele da se obogate. Uskoče kao spekulanti, krenu u vožnju i najverovatnije ih prodaju ubrzo nakon kupovine.
Međutim, čak i kada cena krene naglo prema gore i strmoglavo padne nazad, mnogi ljudi ostanu i nakon tog pada. Otkud mi to znamo? Broj aktivnih novčanika dnevno, koji je otprilike sličan broju korisnika Bitcoin-a, nastavlja da raste. Takođe, nakon svakog balona u istoriji Bitcoin-a, cena se nikada ne vraća na svoju cenu pre balona. Uvek ostane malo višlja. Bitcoin se penje, a svaka masovna spekulativna serija dovodi sve više i više ljudi.
Broj aktivnih Bitcoin novčanika neprekidno raste
„Aktivna adresa“ znači da je neko tog dana poslao Bitcoin transakciju. Donji grafikon je na logaritamskoj skali.
 Izvor: Glassnode
Izvor: GlassnodeCena Bitcoina se neprestano penje
Kroz istoriju Bitcoin-a možemo videti divlje kolebanje cena, ali nakon svakog balona, cena se ostaje višlja nego pre. Ovo je cena Bitcoin-a na logaritamskoj skali.
 Izvor: Glassnode
Izvor: GlassnodeTo pokazuje da se ljudi zadržavaju: potražnja za Bitcoin-om se povećava. Da je svaki masovni rast cena bio samo balon koji su iscenirali prevaranti koji žele brzo da se obogate, cena bi se vratila na nivo pre balona. To se dogodilo sa lalama, ali ne i sa Bitcoin-om.
I zašto se onda cena Bitcoin-a stalno povećava? Sve veći broj ljudi čuva Bitcoin dugoročno – oni razumeju šta Bitcoin može učiniti za njihovu štednju.
Zašto ljudi štede svoj novac u Bitcoin-u umesto na štednim računima, kućama, deonicama ili zlatu? Hajde da pogledajmo sve te metode štednje, i zatim da ih uporedimo sa Bitcoin-om.
Da li je vaš novac siguran u dolarima, kućama, akcijama ili zlatu?
Tokom mnogo godina, to su bile pristojne opcije za štednju. Međutim, sistem koji podržava vrednost svega ovoga je u krizi.
Dolari, Euri, Dinari
Dolari i sve ostale „tradicionalne“ valute koje proizvode vlade, stvorene su da izgube vrednost kroz inflaciju. Banke i tradicionalni monetarni sistem uzrokuju inflaciju stalnim stvaranjem i distribucijom novog novca. Kada Američke Federalne Rezerve objave ciljanu stopu od 2% inflacije, to znači da žele da vaš novac svake godine izgubi 2% od svoje vrednosti. Čak i sa inflacijom od samo 2%, vaša štednja u dolarima izgubiće polovinu vrednosti tokom 40-godišnjeg radnog veka.
Izveštena inflacija se danas opasno povečava, uprkos rastućem „buretu sa barutom“ koji bi mogao da explodira i dovede do masivne hiperinflacije. Što je više valute u opticaju, to je više baruta u buretu.
Naše vlade su ekonomiju napunile valutama da bankarski sistem ne bi propao nakon finansijske krize koja se dogodila 2008. godine. Od tada je većina glavnih centralnih banaka postavila vrlo niske kamatne stope, što pojedincima i korporacijama omogućava dobijanje jeftinijih kredita. To znači da mnogi pojedinci i korporacije podižu ogromne kredite i koriste ih za kupovinu druge imovine poput deonica, umetničkih dela i nekretnina. Sve ovo pozajmljivanje znači da stvaramo tone novog novca i stavljamo ga u opticaj.
Računi za podsticaje (stimulus bills) COVID-19 za 2020. godinu unose trilione u sistem. Ovoliko stvaranje valuta na kraju dovodi do inflacije – velikog gubitka u vrednosti valute.
 Količina američkog dolara u opticaju gotovo se udvostručila od marta 2020. godine. Izvor
Količina američkog dolara u opticaju gotovo se udvostručila od marta 2020. godine. IzvorRačuni za podsticaje su bez presedana, toliko da je neko izmislio meme da opiše ovu situaciju.
Resurs koji vlade mogu da naprave u većem broju da bi platile svoje račune? Ne zvuči kao dobro mesto za štednju novca.
Kuće
Kuće su tokom prošlog veka bile pristojan način štednje novca. Međutim, pad cena nekretnina 2007. godine doveo je do toga da su mnogi vlasnici kuća izgubili svu ušteđevinu.
Danas su kuće gotovo nepristupačne za prosečnog čoveka. Jedan od načina da se ovo izmeri je koliko godišnjih zarada treba prosečnom čoveku da zaradi ekvivalent vrednosti prosečne kuće. Prema CityLab-u, publikaciji Bloomberg-a koja pokriva gradove, porodica može da priuštiti određenu kuću ako košta manje od 2,6 godišnjih prihoda domaćinstva te porodice.
Međutim, prema RZS (Republički zavod za statistiku) prosečan prihod porodičnog domaćinstva u Srbiji iznosi oko 570 EUR mesečno ili otprilike 7.000 EUR godišnje. Nažalost, samo najjeftinija područja van gradova imaju srednje cene kuća od oko 2,6 prosečnih godišnjih prihoda domaćinstva. U većim gradovima poput Beograda i Novog Sada srednja cena kuće je veća od 10 prosečnih godišnjih prihoda jednog domaćinstva.
Ako nekako možete sebi da priuštite kuću, ona bi mogla biti pristojna zaliha vrednosti. Dokle god ne doživimo još jedan krah i izvršitelji zaplene ovu imovinu mnogim vlasnicima kuća.
Akcije
Berza je u prošlosti takođe dobro poslovala. Međutim, sporo i stabilno povećanje tržišta događa se u dosadnom, predvidljivom svetu. Svakog dana vidimo sve manje toga. Nakon ubrzanja korona virusa, videli smo smo najbrži pad američke berze u istoriji od 25% – brži od Velike depresije.
Neki se odlučuju za ulaganje u obveznice i drugu finansijsku imovinu, ali ’prinosi’ za tu imovinu – procenat kamate zarađene na imovinu iz godine u godinu – stalno opada. Sve veći broj odredjenih imovina ima čak i negativne prinose, što znači da posedovanje te imovine košta! Ovo je veliki problem za sve koji se oslanjaju na penziju. Plus, s obzirom na to da su akcije denominovane u tradicionalnim valutama poput dolara i evra, inflacija pojede prinos koji investitor dobije.
Najgore od svega je to što ti isti ekonomski krahovi koji uzrokuju masovna otpuštanja i teško tržište rada takođe znače i nagli pad cena akcija. Čuvanje ušteđevine u akcijama može značiti i gubitak štednje i gubitak posla zbog recesije. Teška vremena mogu da vas prisile da svoje akcije prodate po vrlo malim cenama samo da biste platili svoje račune.
A to nije baš siguran način štednje novca.
Zlato
Vrednost zlata neprekidno se povećavala tokom 5000 godina, obično padajući onda kada berza obećava jače prinose.
Evidencija vrednosti zlata je solidna. Međutim, zlato nosi i druge rizike. Većina ljudi poseduje zlato na papiru. Oni fizički ne poseduju zlato, već ga njihova banka čuva za njih. Zbog toga je zlato veoma podložno konfiskaciji od strane vlade.
Zašto bi vlada konfiskovala nečije zlato, a kamoli u demokratskoj zemlji u „slobodnom svetu“? Ali to se dešavalo i ranije. 1933. godine Izvršnom Naredbom 6102, predsednik Roosevelt naredio je svim Amerikancima da prodaju svoje zlato vladi u zamenu za papirne dolare. Vlada je iskoristila pretnju zatvorom za prikupljanje zlata u fizičkom obliku. Znali su da se zlato više poštuje kao zaliha vrednosti širom sveta od papirnih dolara.
Ako posedujete svoje zlato na nekoj od aplikacija za trgovanje akcijama, možete se kladiti da će vam ga država oduzeti ako joj zatreba. Čak i ako posedujete fizičko zlato, onda ga izlažete mogućnosti krađe – od strane kriminalca ili vaše vlade.
Vaša uštedjevina nije bezbedna.
Rast cena svih gore navedenih sredstava zavisi od našeg trenutnog političkog i ekonomskog sistema koji se nastavlja kao i tokom proteklih 100 godina. Međutim, danas vidimo ogromne pukotine u ovom sistemu.
Sistem ne funkcioniše dobro za većinu ljudi.
Od 1971. plate većine američkih radnika nisu rasle. S druge strane, bogatstvo koje imaju najbogatiji u društvu nalazi se na nivoima koji nisu viđeni više od 80 godina. U međuvremenu, ljudi sve manje i manje veruju institucijama poput banaka i vlada.
 CBPP Nejednakost Bogatstva Tokom Vremena
CBPP Nejednakost Bogatstva Tokom VremenaŠirom sveta možemo videti dokaze o slamanju sistema kroz politički ekstremizam: izbor Trampa i drugih ekstremističkih desničarskih kandidata, Bregzit, pokret Occupy, popularizacija koncepta univerzalnog osnovnog dohotka, povratak pojma „socijalizam“ nazad u modu. Ljudi na svim delovima političkog i društvenog spektra osećaju problematična vremena i posežu za sve radikalnijim rešenjima.
Šta je bolje za štednju od dolara, kuća i akcija?
Pa kako ljudi mogu da štede novac u ovim teškim vremenima? Ili ne koriste tradicionalne valute, ili kupuju sredstva koja će zadržati vrednost u teškim vremenima.
Bitcoin ima najviše potencijala da zadrži vrednost kroz politička i ekonomska previranja od bilo koje druge imovine. Na tom putu će biti rupa na kojima će se rušiti ili pumpati, međutim, njegova svojstva čine ga takvim da će verovatno preživeti previranja kada druga imovina ne bude to mogla.
Šta Bitcoin čini drugačijim?
Bitcoini su retki.
Proces ‘rudarenja’ bitcoin-a, proizvodnju bitcoin-a čini veoma skupom, a Bitcoin protokol ograničava ukupan broj bitcoin-a na 21 milion novčića. To čini Bitcoin imunim na nagle poraste ponude. Ovo se veoma razlikuje od tradicionalnih valuta, koje vlade mogu da štampaju sve više kad god one to požele. Zapamtite, povećanje ponude vrši veliki pritisak na vrednost valute.
Bitcoini nemaju drugu ugovornu stranu.
Bitcoin se takođe razlikuje od imovine kao što su obveznice, akcije i kuće, jer mu nedostaje druga ugovorna strana. Druge ugovorne strane su drugi subjekti uključeni u vrednost sredstva, koji to sredstvo mogu obezvrediti ili vam ga uzeti. Ako imate hipoteku na svojoj kući, banka je druga ugovorna strana. Kada sledeći put dođe do velikog finansijskog kraha, banka vam može oduzeti kuću. Kompanije su kvazi-ugovorne strane akcijama i obveznicama, jer mogu da počnu da donose loše odluke koje utiču na njihovu cenu akcija ili na „neizvršenje“ duga (da ga ne vraćaju vama ili drugim poveriocima). Bitcoin nema ovih problema.
Bitcoin je pristupačan.
Svako sa 5 eura i mobilnim telefonom može da kupi i poseduje mali deo bitcoin-a. Važno je da znate da ne morate da kupite ceo bitcoin. Bitcoin-i su deljivi do 100-milionite jedinice, tako da možete da kupite Bitcoin u vrednosti od samo nekoliko eura. Neuporedivo lakše nego kupovina kuće, zlata ili akcija!
Bitcoin se ne može konfiskovati.
Banke drže većinu vaših eura, zlata i akcija za vas. Većina ljudi u razvijenom svetu veruje bankama, jer većina ljudi koji žive u današnje vreme nikada nije doživela konfiskaciju imovine ili ’šišanje’ od strane banaka ili vlada. Nažalost, postoji presedan za konfiskaciju imovine čak i u demokratskim zemljama sa snažnom vladavinom prava.
Kada vlada konfiskuje imovinu, ona obično ubedi javnost da će je menjati za imovinu jednake vrednosti. U SAD-u 1930-ih, vlada je davala dolare vlasnicima zlata. Vlada je znala da uvek može da odštampa još više dolara, ali da ne može da napravi više zlata. Na Kipru 2012. godine, jedna propala banka je svojim klijentima dala deonice banke da pokrije dolare klijenata koje je banka trebala da ima. I dolari i deonice su strmoglavo opali u odnosu na imovinu koja je uzeta od ovih ljudi.
Doći do bitcoin-a koji ljudi poseduju, biće mnogo teže jer se bitcoin-i mogu čuvati u novčaniku koji ne poseduje neka treća strana, a vi možete čak i da zapamtite privatne ključeve do vašeg bitcoin-a u glavi.
Bitcoin je za štednju.
Bitcoin se polako pokazuje kao najbolja opcija za dugoročnu štednju novca, posebno s obzirom na današnju ekonomsku klimu. Posedovanje čak i malog dela, je polisa osiguranja koja se isplati ako svet i dalje nastavi da ludi. Cena Bitcoin-a u dolarima može divlje da varira u roku od godinu ili dve, ali tokom 3+ godine skoro svi vide slične ili više cene od trenutka kada su ga kupili. U stvari, doslovno niko nije izgubio novac čuvajući Bitcoin duže od 3,5 godine – čak i ako je kupio BTC na apsolutnim vrhovima tržišta.

Imajte na umu da nakon ove tačke ti ljudi više nikada nisu videli rizik od gubitka. Cena se nikada nije smanjila niže od najviše cene u prethodnom ciklusu.
Po čemu se Bitcoin razlikuje od ostalih valuta?
Bitcoin funkcioniše tako dobro kao način štednje zbog svog neobičnog dizajna, koji ga čini drugačijim od bilo kog drugog oblika novca koji je postojao pre njega. Bitcoin je digitalna valuta, prvi i verovatno jedini primer valute koja ima ograničenu ponudu dok radi na otvorenom, decentralizovanom sistemu. Vlade strogo kontrolišu valute koje danas koristimo, poput dolara i eura, i proizvode ih za finansiranje ratova i dugova. Korisnici Bitcoin-a – poput vas – kontrolišu Bitcoin protokol.
Evo šta Bitcoin razlikuje od dolara, eura i drugih valuta:
Bitcoin je otvoren sistem.
Svako može da odluči da se pridruži Bitcoin mreži i primeni pravila softverskog protokola, što je dovelo do vrlo decentralizovanog sistema u kojem nijedan pojedinac ili entitet ne može da blokira transakciju, zamrzne sredstva ili da ukrade od druge osobe.Današnji savremeni bankarski sistem se uveliko razlikuje. Nekoliko banaka je dobilo poverenje da gotovo sve valute, akcije i druge vredne predmete čuvaju na “sigurnom” za svoje klijente. Da biste postali banka, potrebni su vam milioni dolara i neverovatne količine političkog uticaja. Da biste pokrenuli Bitcoin čvor i postali „svoja banka“, potrebno vam je nekoliko stotina dolara i jedno slobodno popodne.
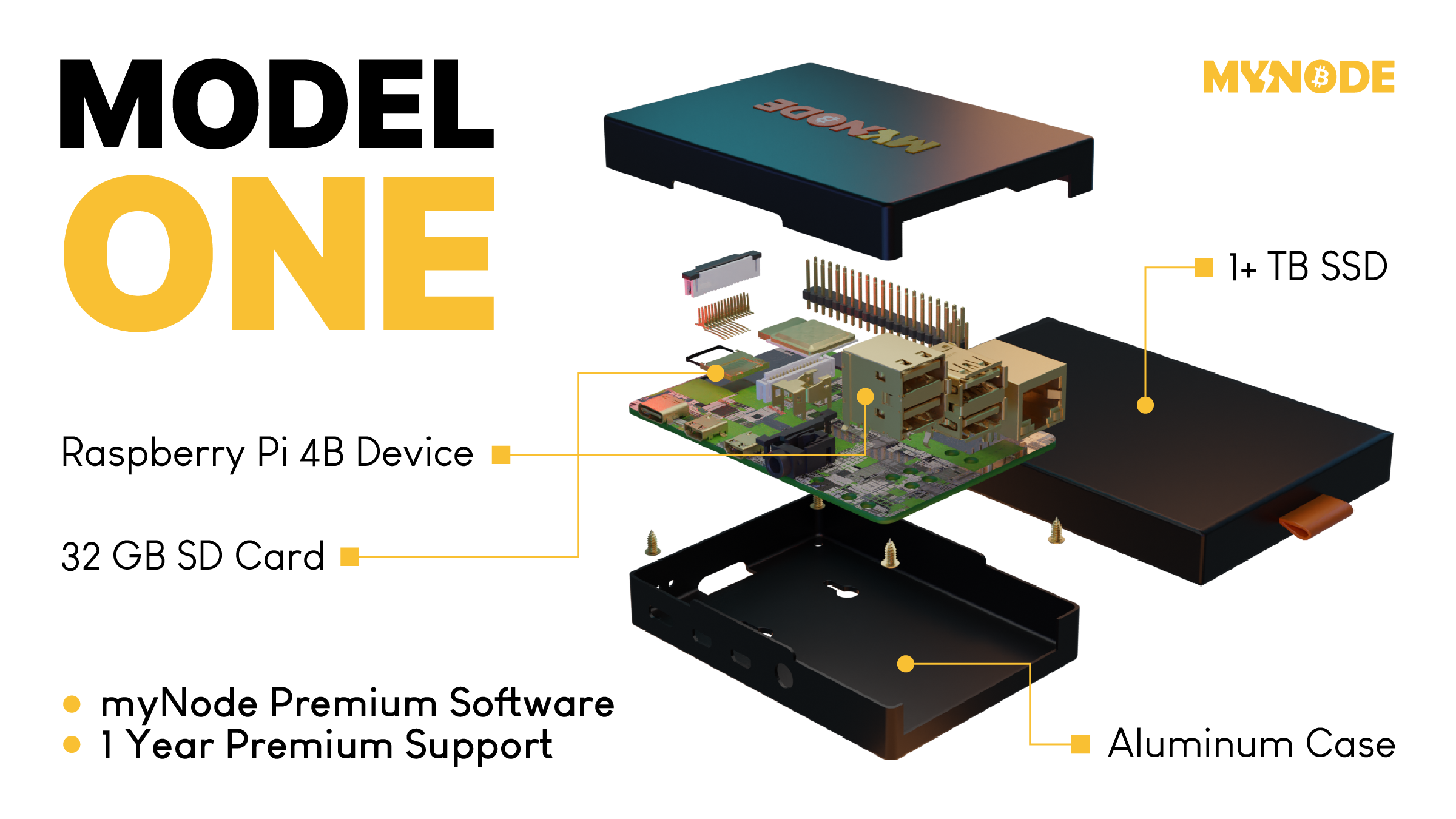 Tako izgleda Bitcoin čvor – Node
MyNode čvor vam omogućava da postanete svoja banka za samo nekoliko minuta.
Tako izgleda Bitcoin čvor – Node
MyNode čvor vam omogućava da postanete svoja banka za samo nekoliko minuta.Bitcoin ima ograničenu ponudu.
Softverski protokol otvorenog koda koji upravlja Bitcoin sistemom ograničava broj novih bitcoin-a koji se mogu stvoriti tokom vremena, sa ograničenjem od ukupno 21.000.000 bitcoin-a. S druge strane, valute koje danas koristimo imaju neograničenu ponudu. Istorija i sadašnje odluke centralnih banaka govore nam da će vlade uvek štampati sve više i više valuta, sve dok valuta ne bude bezvredna. Sve ovo štampanje uzrokuje inflaciju, što pravi štetu običnim radnim ljudima i štedišama.
Tradicionalne valute su dizajnirane tako da opadaju vremenom. Svaki put kada centralna banka kaže da cilja određenu stopu inflacije, oni ustvari kažu da žele da vaš novac svake godine izgubi određeni procenat svoje vrednosti.
Bitcoin-ova ograničena ponuda znači da je on tako dizajniran da raste vremenom kako se potražnja za njim povećava.

Bitcoin putuje oko sveta za nekoliko minuta.
Svako može da pošalje bitcoin-e za nekoliko minuta širom sveta, bez obzira na granice, banke i vlade. Potrebno je manje od minuta da se transakcija pojavi na novčaniku primaoca i oko 60 minuta da se transakcija u potpunosti „obračuna“, tako da primaoc može da bude siguran da su primljeni bitcoin-i sada njegovi (6 konfirmacija bloka). Slanje drugih valuta širom sveta traje danima ili čak mesecima ako se šalju milionski iznosi, a podrazumeva i visoke naknade.
Neke vlade i novinari tvrde da ova sloboda putovanja koju pruža Bitcoin pomaže kriminalcima i teroristima. Međutim, transakciju Bitcoin-a je lakše pratiti nego većinu transakcija u dolarima ili eurima.
Bitcoin se može čuvati na “USB-u”.
Dizajn Bitcoin-a je takav da vam treba samo da čuvate privatni ključ do svojih ‘bitcoin’ adresa (poput lozinke do bankovnih računa) da biste pristupili svojim bitcoin-ima odakle god poželite. Ovaj privatni ključ možete da sačuvate na disku ili na papiru u obliku 12 ili 24 reči na engleskom jeziku. Kao rezultat toga, možete da držite Bitcoin-e vredne milione dolara u svojoj šaci.
Sve ostale valute danas možete ili da strpate u svoj dušek ili da ih poverite banci na čuvanje. Za većinu ljudi koji žive u razvijenom svetu, i koji ne osporavaju autoritet i poverenje u banku, ovo deluje sasvim dobro. Međutim, oni kojima je potrebno da pobegnu od ugnjetavačke vlade ili koji naljute pogrešne ljude, ne mogu verovati bankama. Za njih je sposobnost da nose svoju ušteđevinu bez potrebe za ogromnim koferom neprocenjiva. Čak i ako ne živite na mestu poput ovog, cena Bitcoin-a se i dalje povećava kada ih neko kome oni trebaju kupi.
Kako Bitcoin spašava svet?
Bitcoin, kao ultimativni način štednje, je cakum pakum, ali da li on pomaže u poboljšanju sveta u celini?
Kao što ćete početi da shvatate, ulazeći sve dublje i u druge sadržaje na ovoj stranici, mnogi temeljni delovi našeg današnjeg monetarnog sistema i ekonomije su duboko slomljeni. Međutim, oni koji upravljaju imaju korist od ovakvih sistema, pa se on verovatno neće promeniti bez revolucije ili mirnog svrgavanja od strane naroda. Bitcoin predstavlja novi sistem, sa nekoliko glavnih prednosti:
- Bitcoin popravlja novac, koji je milenijumima služio kao važan alat za rast i poboljšanje društva.
- Bitcoin vraća zdrav razum pozajmljivanju, uklanjanjem apsurdnih situacija poput negativnih kamatnih stopa (gde zajmitelj plaća da bi se zadužio).
- Bitcoin pokreće ulaganja u obnovljive izvore energije i poboljšava energetsku efikasnost u mreži, služeći kao „krajnji kupac“ za sve vrste energije.
Kako mogu da saznam više o Bitcoin-u?
Ovaj članak vam je dao osnovno razumevanje zašto biste trebali razmišljati o Bitcoin-u. Ako želite da saznate više, preporučujem ove resurse:
- Film Bitcoin: Kraj Novca Kakav Poznajemo
- Još uvek je rano za Bitcoin
- Zasto baš Bitcoin?
- Šta je to Bitcoin?
- The Bitcoin Whitepaper ← objavljen 2008. godine, ovo je izložio dizajn za Bitcoin.
-
 @ 2b998b04:86727e47
2025-05-19 21:18:46
@ 2b998b04:86727e47
2025-05-19 21:18:46After the pruning came clarity.\ And after the clarity came a quiet but relentless question:\ What now?
If I wasn’t going back to Web3, if I wasn’t going to pretend anymore — not in faith, not in finance — then I needed to start building again. But this time, with different materials. Different rhythms. A different spirit.
Starting Over on Solid Ground
I’d spent years exploring tokens, networks, and well-intentioned communities. But most of it, I see now, was sand. It moved with the tides. The incentives shifted. The values bent. And when the storms came — personal, financial, spiritual — much of what I’d been part of collapsed or exposed its shallowness.
So I returned to the beginning: What can’t be faked?
That’s where Bitcoin came in — not just as an asset, but as a foundation.\ It taught me cost. Time. Truth. It doesn’t market itself. It just is.\ A system that punishes shortcuts, rewards discipline, and invites peace.
And the more I leaned in, the more I realized:\ This isn’t just money. This is philosophy. This is soil.
Pruned to Plant Again
I used to be a buy-and-hold investor. I still carry those instincts. But in 2020–21, I discovered trading — and with it, a new kind of discipline. Not gambling. Not speculation. Stewardship under pressure. Real-time decision-making with skin in the game.
My grandfather, who passed in the late '90s, probably would’ve looked a little dimly on trading. He lived off his dividends. Stocks he held for decades. He wasn’t chasing. He was rooting. But he would’ve respected the discipline — the clarity — when done right.
He also saw things I didn’t. He once told me I wasn’t raised properly. It hurt at the time, but now I understand. He saw the drift — not just in me, but in the culture. He understood that frugality means nothing if it’s not paired with truth.
I think he would’ve respected what I’m doing now — even if he wouldn't have fully understand it.
What I’m Building Now
-
StartNation – A Bitcoin-aligned equity accelerator. Proof-based. No tokens. No hype.
-
Golden Gate Group Investments – Real estate with a vision to integrate BTC in payments and ownership. Still early. Still real.
-
Blue Planet Ventures – Equities trading with daily proof-of-work and sats-based performance tracking.
-
A garden – Yes, literal food. Soil and seed. Hypdropnics. Bitcoin taught me patience; gardening reinforces it.
I’m not building a brand. I’m building a life. And I’m doing it in public — not to be seen, but to help others see. That it’s possible to step off the hype rails and still thrive.
Bitcoin: The Turning Point
It wasn’t until last fall that Bitcoin truly became central for me.\ Not just part of a portfolio — the lens through which I see capital, time, and truth.
I don’t see it as speculative anymore. I see it as inevitable. In 20–30 years, I believe Bitcoin will be the de facto reserve currency — even if not in name. Those who hold it will steward wealth not because they played the game, but because they opted out of it early.
I’m stacking not to escape — but to prepare. Not to prove I'm right — but to live rightly.
Legacy Without a Platform
I don’t have children.\ But I do have nieces. Nephews. Brothers. Sisters. Cousins. In-Laws.
And I know they’re watching — even if they don’t say it.\ I want to show them that you can live with truth, walk by faith, work with your hands — and still thrive.
I’m not stacking for applause. I’m stacking for legacy.\ I’m building not just for the next quarter — but for the next generation.
And if someone, years from now, asks why I chose this path, I want to say:
Because it was real.\ Because it was proof.\ Because it was built to last.
⚡ If this series has encouraged or challenged you, zap a few sats/bitcoin. It keeps me building.
✍️ Catch up on the full series here:\ \ Part 1: The Drift -> https://primal.net/andrewgstanton/why-i-left-web3-for-proof-of-work-%E2%80%93-part-1%3A-the-drift\ Part 2: The Breaking Point -> https://primal.net/andrewgstanton/why-i-left-web3-for-proof-of-work---part-2%3A-the-breaking-point\ Part 3: The Return -> https://primal.net/andrewgstanton/why-i-left-web3-for-proof-of-work-%E2%80%93-part-3%3A-the-return\ Part 4: Proof Of Work as Philosophy -> https://primal.net/andrewgstanton/why-i-left-web3-for-proof-of-work-%E2%80%93-part-4%3A-proof-of-work-as-philosophy\ Part 5: Building Again (what you are reading now...)
Written with help from ChatGPT (GPT-4), edited and posted by me.
-
-
 @ 1817b617:715fb372
2025-05-19 20:39:28
@ 1817b617:715fb372
2025-05-19 20:39:28Looking to simulate a USDT deposit that appears instantly in a wallet — with no blockchain confirmation, no real spend, and no trace?
You’re in the right place.
🔗 Buy Flash USDT Now This product sends Flash USDT directly to your TRC20, ERC20, or BEP20 wallet address — appears like a real deposit, but disappears after a set time or block depth.
✅ Perfect for: Simulating token inflows Wallet stress testing “Proof of funds” display Flash USDT is ideal for developers, trainers, UI testers, and blockchain researchers — and it’s fully customizable.
🧠 What Is Flash USDT? Flash USDT is a synthetic transaction that mimics a real Tether transfer. It shows up instantly in a wallet balance, and it’s confirmed on-chain — and expires after a set duration.
This makes it:
Visible on wallet interfaces Time-limited (auto-disappears cleanly) Undetectable on block explorers after expiry It’s the smartest, safest way to simulate high-value transactions without real crypto.
🛠️ Flash USDT Software – Your Own USDT Flasher at Your Fingertips Want to control the flash? Run your own operations? Flash unlimited wallets?
🔗 Buy Flash USDT Software
This is your all-in-one USDT flasher tool, built for TRC20, ERC20, and BEP20 chains. It gives you full control to:
Send custom USDT amounts Set custom expiry time (e.g., 30–360 days) Flash multiple wallets Choose between networks (Tron, ETH, BSC) You can simulate any amount, to any supported wallet, from your own system.
No third-party access. No blockchain fee. No trace left behind.
💥 Why Our Flash USDT & Software Stands Out Feature Flash USDT Flash USDT Software One-time flash send ✅ Yes Optional Full sender control ❌ No ✅ Yes TRC20 / ERC20 / BEP20 ✅ Yes ✅ Yes Custom duration/expiry Limited ✅ Yes Unlimited usage ❌ One-off ✅ Yes Whether you’re flashing for wallet testing, demoing investor dashboards, or simulating balance flows, our tools deliver realism without risk.
🛒 Ready to Buy Flash USDT or the Software? Skip the wait. Skip the scammers. You’re one click away from real control.
👉 Buy Flash USDT 👉 Buy Flash USDT Software
📞 Support or live walkthrough?
💬 Telegram: @cryptoflashingtool 📱 WhatsApp: +1 770-666-2531
🚫 Legal Notice These tools are intended for:
Educational purposes Demo environments Wallet and UI testing They are not for illegal use or financial deception. Any misuse is your full responsibility.
Final Call: Need to flash USDT? Want full control? Don’t wait for another “maybe” tool.
Get your Flash USDT or Flashing Software today and simulate like a pro.
🔗 Buy Now → Flash USDT 🔗 Buy Now → Flash USDT Software 💬 Telegram: @cryptoflashingtool 📱 WhatsApp: +1 770-666-2531Looking to simulate a USDT deposit that appears instantly in a wallet — with no blockchain confirmation, no real spend, and no trace?
You’re in the right place.
Buy Flash USDT Now\ This product sends Flash USDT directly to your TRC20, ERC20, or BEP20 wallet address — appears like a real deposit, but disappears after a set time or block depth.
Perfect for:
- Simulating token inflows
- Wallet stress testing
- “Proof of funds” display
Flash USDT is ideal for developers, trainers, UI testers, and blockchain researchers — and it’s fully customizable.
What Is Flash USDT?
Flash USDT is a synthetic transaction that mimics a real Tether transfer. It shows up instantly in a wallet balance, and it’s confirmed on-chain — and expires after a set duration.
This makes it:
- Visible on wallet interfaces
- Time-limited (auto-disappears cleanly)
- Undetectable on block explorers after expiry
It’s the smartest, safest way to simulate high-value transactions without real crypto.
Flash USDT Software – Your Own USDT Flasher at Your Fingertips
Want to control the flash?\ Run your own operations?\ Flash unlimited wallets?
This is your all-in-one USDT flasher tool, built for TRC20, ERC20, and BEP20 chains. It gives you full control to:
- Send custom USDT amounts
- Set custom expiry time (e.g., 30–360 days)
- Flash multiple wallets
- Choose between networks (Tron, ETH, BSC)
You can simulate any amount, to any supported wallet, from your own system.
No third-party access.\ No blockchain fee.\ No trace left behind.
Why Our Flash USDT & Software Stands Out
Feature
Flash USDT
Flash USDT Software
One-time flash send
Yes
Optional
Full sender control
No
Yes
TRC20 / ERC20 / BEP20
Yes
Yes
Custom duration/expiry
Limited
Yes
Unlimited usage
One-off
Yes
Whether you’re flashing for wallet testing, demoing investor dashboards, or simulating balance flows, our tools deliver realism without risk.
Ready to Buy Flash USDT or the Software?
Skip the wait. Skip the scammers.\ You’re one click away from real control.
Support or live walkthrough?
Telegram: @cryptoflashingtool
WhatsApp: +1 770-666-2531
Legal Notice
These tools are intended for:
- Educational purposes
- Demo environments
- Wallet and UI testing
They are not for illegal use or financial deception. Any misuse is your full responsibility.
Final Call:
Need to flash USDT? Want full control?\ Don’t wait for another “maybe” tool.
Get your Flash USDT or Flashing Software today and simulate like a pro.
Telegram: @cryptoflashingtool
WhatsApp: +1 770-666-2531
-
 @ 30b99916:3cc6e3fe
2025-05-19 20:30:52
@ 30b99916:3cc6e3fe
2025-05-19 20:30:52bitcoin #security #vault #veracrypt #powershell
BTCwallet automates running hot and cold storage wallets for multiple Bitcoin wallet applications.

BTCwallet is included with VaultApi and supports Sparrow, Blockstream Green, and just added support for Wasabi wallets.
To launch a wallet application, the command BTCwallet start is executed.
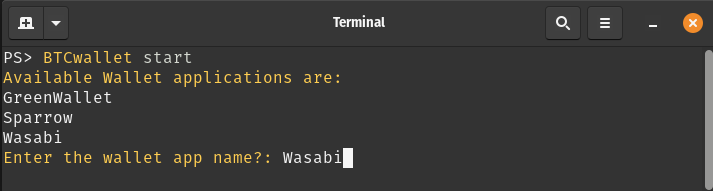
After responding to prompts for launching and initializing the Vault (not shown), the following prompts are presented.
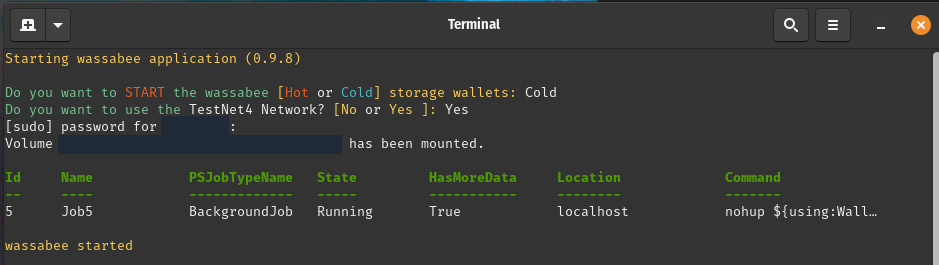
Now the Wasabi GUI application (a.k.a wassabee) is presented.

With the combination of VaultApi and BTCwallet one has a very secure self-hosted password manager along with a very secure way of protecting your Bitcoin wallet's data.
Care to follow me on my journey? If so, then check out the following links.
-
 @ 9be6a199:6e133301
2025-05-19 20:27:20
@ 9be6a199:6e133301
2025-05-19 20:27:20ssdsdsdsdsdsdsd
-
 @ 9be6a199:6e133301
2025-05-19 20:15:18
@ 9be6a199:6e133301
2025-05-19 20:15:18 -
 @ a8d1560d:3fec7a08
2025-05-19 17:28:05
@ a8d1560d:3fec7a08
2025-05-19 17:28:05NIP-XX
Documentation and Wikis with Spaces and Format Declaration
draftoptionalSummary
This NIP introduces a system for collaborative documentation and wikis on Nostr. It improves upon earlier efforts by adding namespace-like Spaces, explicit content format declaration, and clearer separation of article types, including redirects and merge requests.
Motivation
Previous approaches to wiki-style collaborative content on Nostr had two key limitations:
- Format instability – No declared format per event led to breaking changes (e.g. a shift from Markdown to Asciidoc).
- Lack of namespace separation – All articles existed in a global space, causing confusion and collision between unrelated projects.
This NIP addresses both by introducing:
- Spaces – individually defined wikis or documentation sets.
- Explicit per-article format declaration.
- Dedicated event kinds for articles, redirects, merge requests, and space metadata.
Specification
kind: 31055– Space DefinitionDefines a project namespace for articles.
Tags: -
["name", "<space title>"]-["slug", "<short identifier>"]-["description", "<optional description>"]-["language", "<ISO language code>"]-["license", "<license text or SPDX ID>"]Content: (optional) full description or README for the space.
kind: 31056– ArticleAn article in a specific format belonging to a defined space.
Tags: -
["space", "<slug>"]-["title", "<article title>"]-["format", "markdown" | "asciidoc" | "mediawiki" | "html"]-["format-version", "<format version>"](optional) -["prev", "<event-id>"](optional) -["summary", "<short change summary>"](optional)Content: full body of the article in the declared format.
kind: 31057– RedirectRedirects from one article title to another within the same space.
Tags: -
["space", "<slug>"]-["from", "<old title>"]-["to", "<new title>"]Content: empty.
kind: 31058– Merge RequestProposes a revision to an article without directly altering the original.
Tags: -
["space", "<slug>"]-["title", "<article title>"]-["base", "<event-id>"]-["format", "<format>"]-["comment", "<short summary>"](optional)Content: proposed article content.
Format Guidelines
Currently allowed formats: -
markdown-asciidoc-mediawiki-htmlClients MUST ignore formats they do not support. Clients MAY apply stricter formatting rules.
Client Behavior
Clients: - MUST render only supported formats. - MUST treat
spaceas a case-sensitive namespace. - SHOULD allow filtering, browsing and searching within Spaces. - SHOULD support revision tracking viaprev. - MAY support diff/merge tooling forkind: 31058.
Examples
Space Definition
json { "kind": 31055, "tags": [ ["name", "Bitcoin Docs"], ["slug", "btc-docs"], ["description", "Developer documentation for Bitcoin tools"], ["language", "en"], ["license", "MIT"] ], "content": "Welcome to the Bitcoin Docs Space." }Markdown Article
json { "kind": 31056, "tags": [ ["space", "btc-docs"], ["title", "Installation Guide"], ["format", "markdown"] ], "content": "# Installation\n\nFollow these steps to install the software..." }Asciidoc Article
json { "kind": 31056, "tags": [ ["space", "btc-docs"], ["title", "RPC Reference"], ["format", "asciidoc"] ], "content": "= RPC Reference\n\nThis section describes JSON-RPC calls." }MediaWiki Article
json { "kind": 31056, "tags": [ ["space", "btc-docs"], ["title", "Block Structure"], ["format", "mediawiki"] ], "content": "== Block Structure ==\n\nThe structure of a Bitcoin block is..." }Redirect
json { "kind": 31057, "tags": [ ["space", "btc-docs"], ["from", "Getting Started"], ["to", "Installation Guide"] ], "content": "" }Merge Request
json { "kind": 31058, "tags": [ ["space", "btc-docs"], ["title", "Installation Guide"], ["base", "d72fa1..."], ["format", "markdown"], ["comment", "Added step for testnet"] ], "content": "# Installation\n\nNow includes setup instructions for testnet users." }
Acknowledgements
This proposal builds on earlier ideas for decentralized wikis and documentation within Nostr, while solving common issues related to format instability and lack of project separation.
-
 @ 9be6a199:6e133301
2025-05-19 17:24:12
@ 9be6a199:6e133301
2025-05-19 17:24:12this is the content
-
 @ 9be6a199:6e133301
2025-05-19 17:23:23
@ 9be6a199:6e133301
2025-05-19 17:23:23this is the content
-
 @ 3f68dede:779bb81d
2025-05-19 17:14:15
@ 3f68dede:779bb81d
2025-05-19 17:14:15 -
 @ 3f68dede:779bb81d
2025-05-19 17:06:26
@ 3f68dede:779bb81d
2025-05-19 17:06:26 -
 @ 3f68dede:779bb81d
2025-05-19 17:04:13
@ 3f68dede:779bb81d
2025-05-19 17:04:13testing schedule
-
 @ 3f68dede:779bb81d
2025-05-19 17:02:54
@ 3f68dede:779bb81d
2025-05-19 17:02:54testing schedule
-
 @ 3f68dede:779bb81d
2025-05-19 17:02:33
@ 3f68dede:779bb81d
2025-05-19 17:02:33testing
-
 @ 3f68dede:779bb81d
2025-05-19 17:01:57
@ 3f68dede:779bb81d
2025-05-19 17:01:57testing schedule
-
 @ 005bc4de:ef11e1a2
2025-05-19 17:01:54
@ 005bc4de:ef11e1a2
2025-05-19 17:01:54Keys and Religion
Mixing
Normally, I'm not a fan mixing and comparing bitcoinesque things and religion. It's too banal and trite, too easy: the religion of Bitcoin, the allusion of Satoshi the savior, the "Book of Satoshi," even the "Genesis" block. But, today, I'll break my own rule.
Yesterday, I heard a Christian pastor speak of the "keys of the kingdom." My feeling is that, were you to ask the average Christian, "What is the key, or keys, to the kingdom?", and perhaps I'm wrong on this, but I think they'd answer, "Prayer." I've heard it many times, "Prayer is the key to the kingdom." It's an easy mantra to remember. And, prayer is important for a Christian, no question about it. However, Biblically, the phrase "keys of the kingdom" refers to something else.
As the pastor pointed out yesterday, Biblically there are two keys: the binding key and the loosing key. This refers to Matthew 16:19 where Jesus says:
I will give you the keys of the kingdom of heaven; whatever you bind on earth will be bound in heaven, and whatever you loose on earth will be loosed in heaven. Matthew 16:19 (NIV)
For context, back up a few verses. This statement above was made in a conversation between Jesus and his disciple Simon Peter.
15 Jesus asked, “But what about you?” he asked. “Who do you say I am?” 16 Simon Peter answered, “You are the Messiah, the Son of the living God.” 17 Jesus replied, “Blessed are you, Simon son of Jonah, for this was not revealed to you by flesh and blood, but by my Father in heaven. 18 And I tell you that you are Peter, and on this rock I will build my church, and the gates of Hades will not overcome it.
Although brief, this is a deep and rich exchange. Traditionally, this has been viewed as the moment that Christ instituted the Christian church, the passing of power and authority to the early church itself. There has been confusion over it too, particularly the "...on this rock I will build my church..." part of it. Jesus was referring to Simon Peter's statement of faith (...for this was not revealed to you by flesh and blood...) with the "this" being what Peter had just said, "You are the Messiah, the Son of the living God." The church would be built upon the rock of faith in Jesus as the Messiah.
The early Christian church thus established, Jesus instituted what's come to be called the "office of the keys." That is, Jesus grants authority to his "appointees" in the church to carry out his authority. In more practical terms, this is referring to those who have been called into church service, normally priests, to forgive or not forgive sins. When a priest or pastor forgives, or not, it is not that he is doing it by his own right or power. That priest is, after all, yet another sinful man as well. Instead, the priest forgives by Christ's authority which was handed down by Jesus himself in those words to Peter.
To use an analogy, suppose a general had to make a decision about foot soldiers on the front line, waiting there in the trenches. Due to some time constraint, a decision for action was needed imminently. However, suppose the general lacked some bit of information that could only be obtained at the front. So, the general wrote up a communique to the lieutenant stationed at the front saying, "You assess the situation, and you make the call, charge or pull back. I'll support your decision." A courier ran to the front, relayed the message to the lieutenant, and the lieutenant assessed and made the decision. Ultimately, even thought the lieutenant made the decision, the authority behind the decision lay with the general who had transferred his authority to the lieutenant.
This authority or office of the keys is mirrored in John 20:22-23, when the resurrected Jesus appears to his disciples and says, "If you forgive anyone’s sins, their sins are forgiven; if you do not forgive them, they are not forgiven.”
Going just one step further, recall there are two keys involved, binding and loosing, and there are two places involved, earth and heaven. Usually, priests and pastors are "in the business" of forgiving. Penitence or confession, when real, is forgiven. The priest has the authority to forgive, or "loose" the sinner from his wrongdoings here on earth. And, that forgiveness applies to heaven as well, the sin is atoned and reconciled with God.
But, what about when the person is unrepentant, unbothered by what is Biblically sinful, refuses to change his ways, and rather chooses to continue in sinful ways? The "binding" key says that the priest or appointed church leader can hold that person accountable, can bind that person to the sin and separation from God. Normally, we hear of "excommunication" from the church which is formally stating that a person is outside of the church body. The binding keys still bind, both on earth as being outside of the church and in heaven as being separated from God.
And bitcoin?
That's a lot of religion, and heavy religion at that. The question is, what does this have to do with bitcoin?
Keys.
Namely, this is about public and private keys. Loosing and binding keys. A bit more religion, then I'll get back to bitcoin.
Yesterday, the pastor spoke briefly about binding and loosing keys, and this where my thoughts about keys somehow morphed over into bitcoin. For some reason, I pictured Herod's Temple. There had been Solomon's temple, which was destroyed, and then there was Herod's which was known for its beauty and was the one during Jesus's time. But, let's recall the background on this...
The book of Exodus, and others in the Old Testament, outline in detail God's plan for the tabernacle (a traveling tent) and for the temple in Jerusalem.
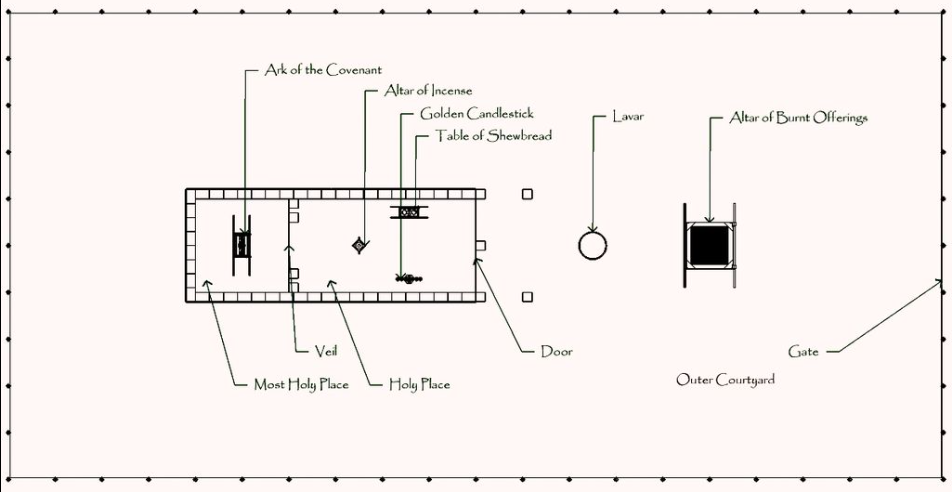
The tabernacle, overhead diagram. Image source: https://en.wikipedia.org/wiki/Tabernacle
You might recall the "history" lesson in Raiders of the Lost Ark. With the tabernacle and temple, one of the purposes was to house the ark of the covenant. Remember that the ark was the golden box that the Israelites carried around containing Moses's stone tablets with the Ten Commandments, some manna, and Aaron's staff. It held great power, God's power, and God literally met and spoke with the Levite priests hovering over the cherubim's wings.
The ark of the covenant. Image source: https://en.wikipedia.org/wiki/Ark_of_the_Covenant
In the tabernacle and temple, the "Holy of Holies" was a room, separated by a heavy curtain. It was off limits to all because it was, well, holy of holies. A heavy curtain divided the Holy of Holies, or the "Most Holy Place", from the less-holy, "Holy Place."
Once a year, on the Day of Atonement, one person, the chief priest, was allowed to walk into the Holy of Holies. He would sprinkle the blood of a sacrificed animal onto the ark. This was done for the forgiveness of the people's sins. Although this was pre-Jesus's words, this was using the loosing keys and was loosing sin.
This was serious business and was taken seriously. For instance, the priests Nadab and Abihu improperly performed their sacrificial duties, they messed up the procedure, and were consumed by fire. Priesthood was a dangerous occupation, one slip up and you were scorched.
 The second temple, "Herod's Temple". Image source: https://en.wikipedia.org/wiki/Second_Temple
The second temple, "Herod's Temple". Image source: https://en.wikipedia.org/wiki/Second_TempleBack to keys...
Yesterday, for some reason when I heard about binding and loosing keys, I imagined the chief priest standing in front of the curtain. I imagined him taking a deep breath, collecting his thoughts, getting ready to go in. It had to be intimidating.
As he stood there, in my mind, he and everyone else was shut out. The Most Holy Place was bound and locked. Walking in meant getting scorched (again, the end of Raiders of the Lost Ark). Yet, that priest had the loosing key. He had, first, permission as chief priest to enter on the Day of Atonement, secondly, he had the sacrificial blood to loose sins. Although the binding key had locked the Holy of Holies and thus bound the sins of the people, the loosing key was about to loose their sins.
Cryptographic keys
And back to bitcoin...
Bitcoin, and cryptography in general, operate on public and private keys. Any flavor of "cryptocurrency", or even Nostr, has public and private keys. In a way, these are binding and loosing keys.
Say you have 1.0 BTC (that's 100,000,000 sats 😀). That BTC exists as a UTXO which can be seen by anyone viewing your public address. In this way, your bitcoin public key is your binding key...that UTXO, that bitcoin, is bound to your public key...it is locked in place behind that heavy curtain. It will be there forever, unless there is an intervention...
You also have your private key, your loosing key. You can apply your private key to loose that UTXO, that bitcoin, and to send it along to wherever.
This is like law and gospel: sin is binding, however Jesus frees it. A bitcoin UTXO is bound until a private key looses it.
Nostr offers a somewhat similar illustration. You have an npub publicly and and nsec secretly or privately. If you were to write a note, your private nsec is needed as a loosing key to free that message, to broadcast it to the world. Once broadcast, it can be seen by all, however it is still inextricably bound or tied to your public key (your npub). Your npub is your binding key and your message is bound to it.
Summed
I'm not sure this binding and loosing keys in religion, and public and private keys in cryptography is the best comparison in the world. It's probably a terrible comparison. But, this is what came to my mind yesterday.
And, so, the mixing of religion and bitcoin is now officially over.
-
 @ 3f68dede:779bb81d
2025-05-19 17:01:19
@ 3f68dede:779bb81d
2025-05-19 17:01:19testing schedule
-
 @ 3f68dede:779bb81d
2025-05-19 17:00:18
@ 3f68dede:779bb81d
2025-05-19 17:00:18testing schedule
-
 @ 3f68dede:779bb81d
2025-05-19 16:59:50
@ 3f68dede:779bb81d
2025-05-19 16:59:50testing schedule
-
 @ 866e0139:6a9334e5
2025-05-19 21:39:26
@ 866e0139:6a9334e5
2025-05-19 21:39:26Autor: Ludwig F. Badenhagen. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie auch in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Wer einhundert Prozent seines Einkommens abgeben muss, ist sicher ein Sklave, oder? Aber ab wieviel Prozent Pflichtabgabe ist er denn kein Sklave mehr? Ab wann ist er frei und selbst-bestimmt?
Wer definieren möchte, was ein Sklave ist, sollte nicht bei Pflichtabgaben verweilen, denn die Fremdbestimmtheit geht viel weiter. Vielfach hat der gewöhnliche Mensch wenig Einfluss darauf, wie er und seine Familie misshandelt wird. Es wird verfügt, welche Bildung, welche Nahrung, welche Medikamente, welche Impfungen und welche Kriege er zu erdulden hat. Hierbei erkennt der gewöhnliche Mensch aber nur, wer ihm direkt etwas an-tut. So wie der Gefolterte bestenfalls seinen Folterer wahrnimmt, aber nicht den, in dessen Auftrag dieser handelt, so haben die vorbezeichnet Geschädigten mit Lehrern, „Experten“, Ärzten und Politikern zu tun. Ebenfalls ohne zu wissen, in wessen Auftrag diese Leute handeln. „Führungssysteme“ sind so konzipiert, dass für viele Menschen bereits kleinste wahrgenommene Vorteile genügen, um einem anderen Menschen Schlimmes anzutun.
Aber warum genau wird Menschen Schlimmes angetan? Die Gründe dafür sind stets dieselben. Der Täter hat ein Motiv und Motivlagen können vielfältig sein.
Wer also ein Motiv hat, ein Geschehen zu beeinflussen, motiviert andere zur Unterstützung. Wem es gelingt, bei anderen den Wunsch zu erwecken, das zu tun, was er möchte, ist wirklich mächtig. Und es sind die Mächtigen im Hintergrund, welche die Darsteller auf den Bühnen dieser Welt dazu nutzen, die Interessen der wirklich Mächtigen durchzusetzen. Insbesondere die letzten fünf Jahre haben eindrucksvoll gezeigt, wie willfährig Politiker, Ärzte, Experten und viele weitere ihre jeweiligen Aufträge gegen die Bevölkerung durchsetz(t)en.
Und so geschieht es auch beim aktuellen Krieg, der stellvertretend auf dem europäischen Kontinent ausgetragen wird. Parolen wie „nie wieder Krieg“ gehören der Vergangenheit an. Stattdessen ist nunmehr wieder der Krieg und nur der Krieg geeignet, um „Aggressionen des Gegners abzuwehren“ und um „uns zu verteidigen“.
Das hat mindestens drei gute Gründe:
- Mit einem Krieg können Sie einem anderen etwas wegnehmen, was er freiwillig nicht herausrückt. Auf diese Weise kommen Sie an dessen Land, seine Rohstoffe und sein Vermögen. Sie können ihn beherrschen und Ihren eigenen Einfluss ausbauen. Je mehr Ihnen gehört, um so besser ist das für Sie. Sie müssen sich weniger abstimmen und Widersacher werden einfach ausgeschaltet.
- Wenn etwas über einen langen Zeitraum aufgebaut wurde, ist es irgendwann auch einmal fertig. Um aber viel Geld verdienen und etwas nach eigenen Vorstellungen gestalten zu können, muss immer wieder etwas Neues erschaffen werden, und da stört das Alte nur. Demzufolge ist ein Krieg ein geeignetes Mittel, etwas zu zerstören. Und das Schöne ist, dass man von Beginn an viel Geld verdient. Denn man muss dem indoktrinierten Volk nur vormachen, dass der Krieg „unbedingt erforderlich“ sei, um das Volk dann selbst bereitwillig für diesen Krieg bezahlen und auch sonst engagiert mitwirken zu lassen. Dann kann in Rüstung und „Kriegstauglichkeit“ investiert werden. Deutschland soll dem Vernehmen nach bereits in einigen Jahren „kriegstauglich“ sein. Der Gegner wartet sicher gerne mit seinen Angriffen, bis es so weit ist.
- Und nicht zu vergessen ist, dass man die vielen gewöhnlichen Menschen loswird. Schon immer wurden Populationen „reguliert“. Das macht bei Tieren ebenfalls so, indem man sie je nach „Erfordernis“ tötet. Und bei kollabierenden Systemen zu Zeiten von Automatisierung und KI unter Berücksichtigung der Klimarettung wissen doch mittlerweile alle, dass es viel zu viele Menschen auf dem Planeten gibt. Wenn jemand durch medizinische Misshandlungen oder auch durch einen Krieg direkt stirbt, zahlt dies auf die Lösung des Problems ein. Aber auch ein „Sterben auf Raten“ ist von großem Vorteil, denn durch die „fachmännische Behandlung von Verletzten“ bis zu deren jeweiligen Tode lässt sich am Leid viel verdienen.
Sie erkennen, dass es sehr vorteilhaft ist, Kriege zu führen, oder? Und diese exemplarisch genannten drei Gründe könnten noch beliebig erweitert werden.
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes.
Das Einzige, was gegen Kriegsereignisse sprechen könnte, wäre, dass man selbst niemandem etwas wegnehmen möchte, was ihm gehört, und dass man seinen Mitmenschen nicht schaden, geschweige denn diese verletzen oder gar töten möchte.
In diesem Zusammenhang könnte man auch erkennen, dass die, die nach Krieg rufen, selbst nicht kämpfen. Auch deren Kinder nicht. Man könnte erkennen, dass man selbst nur benutzt wird, um die Interessen anderer durchzusetzen. Wie beim Brettspiel Schach hat jede Figur eine Funktion und keinem Spieler ist das Fortbestehen eines Bauern wichtig, wenn seine Entnahme dem Spielgewinn dient. Wer Krieg spielt, denkt sicher ähnlich.
Meine beiden Großväter waren Soldaten im zweiten Weltkrieg und erlebten die Grausamkeiten des Krieges und der Gefangenschaft so intensiv, dass sie mit uns Enkeln zu keiner Zeit hierüber sprechen konnten, da sie wohl wussten, dass uns allein ihre Erzählungen zutiefst traumatisiert hätten. Die Opas waren analog dem, was wir ihnen an Information abringen konnten, angeblich nur Sanitäter. Sanitäter, wie auch die meisten Großväter aus der Nachbarschaft. Wer aber jemals beobachten konnte, wie unbeholfen mein Opa ein Pflaster aufgebracht hat, der konnte sich denken, dass seine vermeintliche Tätigkeit als Sanitäter eine Notlüge war, um uns die Wahrheit nicht vermitteln zu müssen.
Mein Opa war mein bester Freund und mir treibt es unverändert die Tränen in die Augen, sein erlebtes Leid nachzuempfinden. Und trotz aller seelischen und körperlichen Verletzungen hat er nach seiner Rückkehr aus der Kriegshölle mit großem Erfolg daran gearbeitet, für seine Familie zu sorgen.
Manchmal ist es m. E. besser, die Dinge vom vorhersehbaren Ende aus zu betrachten, um zu entscheiden, welche Herausforderungen man annimmt und welche man besser ablehnt. Es brauchte fast 80 Jahre, um die Deutschen erneut dafür zu begeistern, Ihre Leben „für die gute Sache“ zu opfern. Was heutzutage aber anders ist als früher: Einerseits sind die Politiker dieser Tage sehr durchschaubar geworden. Aber in einem ähnlichen Verhältnis, wie die schauspielerischen Leistungen der Politiker abgenommen haben, hat die Volksverblödung zugenommen.
Denken Sie nicht nach. Denken Sie stattdessen vor. Und denken Sie selbst. Für sich, Ihre Lieben und alle anderen Menschen. Andernfalls wird die Geschichte, so wie sie von meinen Opas (und Omas) erlebt wurde, mit neuen Technologien und „zeitgemäßen Methoden“ wiederholt. Dies führt zweifelsfrei zu Not und Tod.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 662f9bff:8960f6b2
2025-05-19 15:11:25
@ 662f9bff:8960f6b2
2025-05-19 15:11:25Let's start with some important foundational thinking - based on natural law. Money should be separate from the State - if not history shows that governments and human greed will always take over and manipulate the system in their favour and the expense of their populations. For extensive references, read The Sovereign Individual and The Creature from Jeckyll Island.
-
The Separation of State and Money is the most important thing you can listen to this week. Thanks to Allen Farrington - his paper is here for those who prefer to read. Wake up, folks!
-
The American Forefathers knew this when the wrote the American Constitution. Thomas Jefferson said: “If the American people ever allow private banks to control the issue of their currency first by inflation then by deflation the banks and corporations that will grow up around them will deprive the people of all property until their children wake up homeless on the continent their Fathers conquered... I believe that banking institutions are more dangerous to our liberties than standing armies... The issuing power should be taken from the banks and restored to the people to whom it properly belongs.” Mark Moss explains it well here. Charlie Robinsons take here.
The situation in Canada explifies the issues
Governments have have long used "international economic sanctions" against other nations to enforce their positions. Now in Canada, and soon in your country too, they are applying such sanctions their own citizens - disconnecting them from the financial system and removing their ability to use their own life savings as they wish. Canadians spoke with their money - in one week they raised more money in support of the truckers for peaceful protest than were raised in support of all Canadian political parties in the election of last year - only to have it confiscated and blocked by those politicians.
-
CPL. Daniel Bulford (Justin Trudeau's body guard) is particularly clear and eloquent - https://www.facebook.com/watch/?v=3123688351279364
-
Nick & Greg (two Canadians in Canada) explain the situation to Peter McCormack - https://youtu.be/QBWYp-cBr4o
-
Dr Jordan Peterson and Dr Julie Ponesse (also Canadians in Canada) speak openly about what is going on https://t.co/2T7A4VEek1
-
Even Canadians living in China speak up: https://www.youtube.com/watch?v=xvDvJWdlD1E
Meanwhile in Turkey...
Joe Blogs has been giving blow by blow updates of the deteriorating sitation over the last weeks. What is happening to Turkey will come to many countries - sooner than you might imagine. Watch and learn here, here and here - more on his channel.
EU Citizens should be aware and lobby their MPs
Dropping of all C-19 restrictions is a tactic to stop people thinking about them; meanwhile the politicians are taking steps to get all of the emergency restrictions codified into normal law so that they can be deployed on you any time or all the time in future.\ Act now - or lose all freedoms - your choice - watch here or click below for the explainer.
More on war - recall our discussion last week
War steals and destroys the wealth of generations. We have been here before - remember World Wars 1 and 2...
-
Dr Mattias Desmet explains how mass formation psychosis happens and how he became aware: https://www.youtube.com/watch?v=CRo-ieBEw-8
-
Be aware of this well known and much abused psycholgical experiment - rats in a cage - explained by Dr Christ Martensen: https://www.youtube.com/watch?v=7kSBdMXQkPI
To remain silent is wrong - to deny the rights of others to discuss and challenge (and even to punish or coerce them) is a crime in support of the biger crime. Each of us has a choice - choose wisely.
Could you have known about this?
"The Matrix is a system, Neo. That system is our enemy. But when you're inside, you look around, what do you see? Businessmen, teachers, lawyers, carpenters. The very minds of the people we are trying to save. But until we do, these people are still a part of that system and that makes them our enemy. You have to understand, most of these people are not ready to be unplugged. And many of them are so inert, so hopelessly dependent on the system that they will fight to protect it."
"Unfortunately, no one can be told what the Matrix is. You have to see it for yourself."
A closing thought...
Look closely at the cover of the Economist magazine released in December 2018 - The World in 2019 - see how many of those things have already come true.
In case this is too difficult for you - some things to note: Four horsemen of the apacalypse, Statue of Liberty wearing a facemask, Vetruvian Man with QR code (Vaccine passport), DNA mark on his arm, wearing virtual reality glasses... The animal bottom right is a Pangolin. Scales of Justice are well tipped/skewed, facial recognition, electric cars, Putin's pipelines, China and Brexit feature highly along with the lieing media (Pinnochio) and #metoo. I smell Predictive Programming.
- More insights in the explainer here (backup copy here) - including why it is backwards...
That's it!
No one can be told what The Matrix is.\ You have to see it for yourself.**
Do share this newsletter with any of your friends and family who might be interested.
You can also email me at: LetterFrom@rogerprice.me
💡Enjoy the newsletters in your own language : Dutch, French, German, Serbian, Chinese Traditional & Simplified, Thai and Burmese.
-
-
 @ 4c96d763:80c3ee30
2025-05-19 20:56:26
@ 4c96d763:80c3ee30
2025-05-19 20:56:26Changes
William Casarin (19):
- dave: add screenshot to readme
- dave: fix image in readme
- columns: remove spamming info logs about writing to cache
- columns: never truncate notes you're replying to
- windows: don't show terminal window
- mention: show username instead of display_name
- chrome: switch from ALPHA to BETA
- ui: make post replies selectable
- dave: include anonymous user identifier in api call
- dave: add trial mode
- dave: fix sidebar click
- dave: nudge avatar when you click
- dave: hide media in dave note previews
- chrome: fix theme persistence
- ui: fix a bunch of missing hover pointers
- Release Notedeck Beta v0.4.0
- release: changelog
- timeline: show media on universe timeline
- clippy: fix lint related to iterator
kernelkind (28):
- add
trust_media_from_pk2method - add hashbrown
- introduce & use
JobPool - introduce JobsCache
- add blurhash dependency
- introduce blur
- note: remove unnecessary derive macros from
NoteAction - propagate
JobsCache ImagePulseTint->PulseAlpha- images: move fetch to fn
- add
TexturesCache - images: make
MediaCacheholdMediaCacheType - images: make promise payload optional to take easily
- post: unnest
- notedeck_ui: move carousel to
note/media.rs - note media: only show full screen when loaded
- note media: unnest full screen media
- pass
NoteActionby value instead of reference - propagate
Imagesto actionbar - add one shot error message
- make
WidgetimplProfilePicmutably - implement blurring
- don't show zap button if no wallet
- display name should wrap
- make styled button toggleable
- method to get current default zap amount
- add
CustomZapView - use
CustomZapView
pushed to notedeck:refs/heads/master
-
 @ c6d8334c:30883d6d
2025-05-19 15:02:01
@ c6d8334c:30883d6d
2025-05-19 15:02:01#KIBedenken - Bewusstsein
Einen wichtigen Impuls über KI nachzudenken lieferte vor einiger Zeit Yuval Noah Harari an der University of Cambridge am Ende eines Podiumsgesprächs hier ab 1:15 h auf youtube:
Ich denke, wir müssen die Frage des Bewusstseins in den Mittelpunkt der Diskussion stellen. Es gibt eine riesige, riesige Verwirrung in der Terminologie, auch in der Welt der KI, zwischen Bewusstsein und Intelligenz. Aber es sind zwei verschiedene Dinge. Intelligenz ist die Fähigkeit, Probleme zu lösen und Ziele zu erreichen. Bewusstsein ist die Fähigkeit, Dinge zu fühlen, wie Schmerz oder Freude oder Liebe oder Hass. Wir neigen dazu, die beiden zu verwechseln, weil bei Menschen und auch bei anderen Säugetieren, Vögeln und anderen Tieren Bewusstsein und Intelligenz zusammengehören. Wir lösen Probleme durch unsere Gefühle. Computer waren bisher sehr anders. Sie sind in einigen Bereichen bereits intelligenter als wir, haben aber, soweit wir wissen, kein Bewusstsein. Soweit wir wissen, können sie überhaupt keinen Schmerz, keine Freude, keine Liebe oder keinen Hass empfinden. Niemand weiß, was in Zukunft passieren wird. Es gibt Modelle und Theorien, die argumentieren, dass KIs irgendwann auch bewusst oder empfindsam werden. Sie werden anfangen, Dinge zu fühlen. Sie werden anfangen, Schmerz oder Liebe oder Hass zu empfinden. Es gibt andere Modelle und Theorien, die sagen, nein. Sie könnten weit intelligenter werden als wir und immer noch null Bewusstsein haben. Das kann in der Evolution des Lebens sein. Wenn man darüber nachdenkt, die lange Entwicklung von Milliarden von Jahren der Evolution. Die Entwicklung der Intelligenz ist im Falle von Tieren wie uns und Schimpansen und Hunden und Schweinen und so weiter durch die Entwicklung des Bewusstseins verlaufen. Aber das ist kein universelles Gesetz der Evolution der Intelligenz. Vielleicht gibt es alternative Wege, die zu Superintelligenz ohne jegliches Bewusstsein führen. Einfach einen anderen, einen fremden Weg gehen. Und wir könnten an einen Punkt gelangen, an dem sie superintelligent sind und trotzdem null Bewusstsein haben. Und die Gefahr besteht dann darin, dass sie nicht nur die menschliche Zivilisation zerstören könnten, sondern das ganze Licht des Bewusstseins, um das gesamte ökologische System nach ihren Bedürfnissen umzugestalten, wofür sie kein Bewusstsein brauchen. Sie funktionieren auf eine völlig andere Weise. Sie könnten sich sogar von der Erde auf andere Planeten, auf andere Galaxien ausbreiten. Sie werden das Universum mit Intelligenz füllen, aber es wird ein völlig dunkles Universum ohne Bewusstsein sein. Wieder hohe Intelligenz, fähig, Raumschiffe zu bauen, die mit Lichtgeschwindigkeit fliegen und was auch immer, aber es gibt null Gefühl. Niemand, keine Entität fühlt Schmerz oder Freude, Liebe oder Hass. Für mich ist das ein schreckliches Szenario. Das schlimmste Szenario von allen ist dies. Dass wir ein Universum voller Intelligenz und völlig ohne Bewusstsein haben werden, denn ich denke, dass von den beiden das Bewusstsein weitaus wichtiger, weitaus wertvoller ist. Und es ist eine gute Erinnerung daran, dass wir das zumindest heute mit vielen anderen Tieren teilen, aber nicht mit den Computern, nicht mit den KIs. Wir sind also immer noch im selben Team wie die Würmer und die Affen, nicht im selben Team wie die Computer.
Ich denke, hier wird eine Spur gelegt, die sich unterscheidet von der reinen Funktion von KI zur intelligenten Verbesserung und Unterstützung von Lernprozessen oder vielfältigem Kompetenzerwerb hin zur Selbstreflexion der Lernenden. Auch im Blick auf (religionsbezogene) Bildung kennen wir den Mensch nicht nur biologisch, wie die Würmer und Affen sondern auch ausgestattet mit Würde, Entscheidungsfreiheit und als Beziehungswesen, das auf ein Gegenüber ausgerichtet sein kann und, wie Harari sagt, nicht im selben Team wie die Computer spielt. Sinn, Seele und Verstand erhalten wir weder aus uns selbst heraus noch von einer wie auch immer gearteten Intelligenz. Liebe, Gnade, Hoffnung, Frieden, Gemeinschaft, Trost, Zuversicht und viele weiteren lebensbedeutsame Erfahrungen gewinnen im Angesicht von Maschinen aus meiner Sicht an elementarer Bedeutung.
-
 @ 9223d2fa:b57e3de7
2025-05-19 15:01:19
@ 9223d2fa:b57e3de7
2025-05-19 15:01:196,323 steps
-
 @ d41bf82f:ed90d888
2025-05-19 20:31:54
@ d41bf82f:ed90d888
2025-05-19 20:31:54“ประเด็นแท้จริงคือเรื่องของการควบคุม—อินเทอร์เน็ตแพร่ขยายกว้างไกลเกินกว่าที่รัฐบาลใดจะครอบงำได้โดยง่าย ด้วยการสร้างเขตเศรษฐกิจระดับโลกที่ไร้รอยต่อ ไม่ขึ้นต่ออธิปไตย และอยู่นอกเหนือการควบคุม อินเทอร์เน็ตจึงตั้งคำถามต่อแนวคิดของรัฐชาติในตัวมันเอง” — JOHN PERRY BARLOW
บทนี้เริ่มต้นด้วยการวิพากษ์แนวคิด ทางด่วนข้อมูล ว่าเป็นคำอุปมาอุปมัยที่ยังยึดติดกับโลกยุคอุตสาหกรรม เพราะเศรษฐกิจยุคสารสนเทศไม่ใช่แค่โครงสร้างพื้นฐานสำหรับขนส่งข้อมูล แต่คือ จุดหมายปลายทาง ใหม่ในตัวเอง นั่นคือ ไซเบอร์สเปซ —ดินแดนที่ก้าวข้ามขอบเขตทางภูมิศาสตร์โดยสิ้นเชิง
ไซเบอร์สเปซคือพื้นที่ใหม่ของปฏิสัมพันธ์ทางสังคม เศรษฐกิจ และการเมือง ซึ่งไม่สามารถควบคุมโดยรัฐชาติแบบเดิมได้อีกต่อไป ผู้เขียนยกคำของ John Perry Barlow ที่เปรียบไซเบอร์สเปซเป็น “ดินแดนแห่งเสรีภาพ” ที่ไม่ยึดโยงกับสถานที่จริง และเปิดโอกาสให้ทุกคนแสดงความคิดเห็นได้อย่างไร้การควบคุม
การเปลี่ยนผ่านนี้ส่งผลกระทบรุนแรงต่อโครงสร้างของเศรษฐกิจแบบเดิม การเข้าถึงข้อมูลอย่างรวดเร็วแบบไร้ขอบเขตเปรียบเสมือนตัวทำละลายที่กัดกร่อนต้นทุนของสถาบันขนาดใหญ่ ทั้งภาครัฐและเอกชน ไมโครโพรเซสซิงจะเปลี่ยนรูปแบบขององค์กรและแนวคิดเรื่องสถานที่ในทางเศรษฐกิจอย่างสิ้นเชิง
ตลอดประวัติศาสตร์ เศรษฐกิจผูกติดกับพื้นที่ทางภูมิศาสตร์ การเดินทางเป็นเรื่องยากและจำกัด การค้าขายส่วนใหญ่เกิดในระดับท้องถิ่น ภาษา วัฒนธรรม และภูมิประเทศเป็นอุปสรรคทางการเมืองเสมอ จนถึงกับที่ผู้เขียนกล่าวว่า การเมืองทั้งหมดเป็นเรื่องท้องถิ่น
แต่เทคโนโลยีสมัยใหม่กำลังเปลี่ยนสมการนี้ การสื่อสารและขนส่งที่รวดเร็วทำให้ผู้มีความสามารถสามารถเลือกสถานที่อยู่อาศัยหรือทำงานได้อย่างเสรี ลดอำนาจต่อรองของรัฐบาลในพื้นที่นั้นลง เพราะคนสามารถ “หนี” ได้ง่ายขึ้น หากรัฐบาลกดขี่หรือรีดไถ
แม้อินเทอร์เน็ตยุคแรกจะดูธรรมดา เช่น ใช้อ่านบทความหรือสั่งซื้อสินค้า แต่ศักยภาพที่แท้จริงของเศรษฐกิจไซเบอร์นั้นยิ่งใหญ่มาก ผู้เขียนเสนอว่ามันจะพัฒนาเป็นสามขั้น: 1. ขั้นพื้นฐาน: อินเทอร์เน็ตเป็นเพียงช่องทางเพิ่มประสิทธิภาพธุรกิจแบบเดิม (เช่น เว็บขายสินค้าขายของออนไลน์ เช่น อเมซอน) 2. ขั้นพัฒนา: การเกิดขึ้นของเงินดิจิทัลที่เข้ารหัสและไม่สามารถติดตามได้ จะปลดปล่อยธุรกรรมจากการควบคุมและการจัดเก็บภาษีของรัฐ 3. ขั้นก้าวหน้า: ไซเบอร์สเปซจะมีระบบเศรษฐกิจ กฎหมาย และกลไกคุ้มครองของตัวเอง ปราศจากการควบคุมจากรัฐบาลใด ๆ
ในโลกใหม่นี้ Sovereign Individual หรือ “ปัจเจกผู้มีอธิปไตย” จะสามารถสร้างความมั่งคั่งและดำเนินกิจกรรมในไซเบอร์สเปซได้อย่างเป็นอิสระ โดยไม่ต้องอิงรัฐชาติ รัฐจึงจะถูกบีบให้ลดขนาดและเปลี่ยนบทบาทจากผู้ใช้อำนาจกลายเป็นผู้ให้บริการที่ต้องแข่งขันเพื่อความพึงพอใจของพลเมือง
สามารถไปติดตามเนื้อหาแบบ short vdo ที่สรุปประเด็นสำคัญจากแต่ละบท พร้อมกราฟิกและคำอธิบายกระชับ เข้าใจง่าย ได้ที่ TikTok ช่อง https://www.tiktok.com/@moneyment1971
-
 @ cae03c48:2a7d6671
2025-05-19 18:29:07
@ cae03c48:2a7d6671
2025-05-19 18:29:07Bitcoin Magazine

Bitcoin Records Highest Weekly Close Above $106KBitcoin has officially recorded its highest-ever weekly candle close, finishing the week at $106,516. The milestone was achieved on Sunday evening, marking a notable moment in Bitcoin’s ongoing price history and underscoring growing institutional and retail interest.
JUST IN: $107,000 #Bitcoin
 pic.twitter.com/Xt1JLm0Ke6
pic.twitter.com/Xt1JLm0Ke6— Bitcoin Magazine (@BitcoinMagazine) May 19, 2025
This weekly close sets a new benchmark for BTC’s price performance and positions the asset in a historically rare range. As of Monday, Bitcoin is trading at $102,924, reflecting typical price movement following a new high as markets adjust to key levels.
Historical data helps illustrate the significance of this moment. According to an analysis shared by on-chain researcher Dan, Bitcoin has closed above $106,439 only once—this week—accounting for just 0.02% of its entire trading history. Closures above $100,000 have occurred in only 40 days total. Even levels like $75,000 and $50,000 remain relatively uncommon in Bitcoin’s lifespan, appearing on just 181 and 586 days, respectively.
— Dan (@robustus) May 19, 2025
This data highlights how current prices place Bitcoin in a historically narrow range of time — a reflection of the long-term upward trend of the asset over the past decade. For market participants, this type of price action often serves as an indicator of continued momentum and interest in Bitcoin’s role as a digital store of value.
The broader Bitcoin ecosystem continues to show strength, with on-chain metrics reflecting growing user engagement and long-term holder confidence. Notably, activity on the Bitcoin network remains elevated, with transaction volumes and address growth signaling continued adoption. Analysts are closely watching inflows into Bitcoin-focused ETFs and the behavior of long-term holders, both of which are key indicators of sustained interest and belief in Bitcoin’s long-term value.
bitcoin just had its all-time high weekly candle close at $106,500 pic.twitter.com/FuqqptHEmA
— Alex Thorn (@intangiblecoins) May 19, 2025
Some traders are watching the $100,000 level closely as a key psychological and technical zone. Bitcoin’s ability to maintain this level following a record weekly close could be important in setting the tone for the weeks ahead.
While near-term price movements are always part of market dynamics, the latest close represents a milestone in Bitcoin’s history. It reaffirms the asset’s resilience and ongoing relevance in the global financial landscape.
This post Bitcoin Records Highest Weekly Close Above $106K first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ 82a7a1ff:2c1e9cdf
2025-05-19 18:18:31
@ 82a7a1ff:2c1e9cdf
2025-05-19 18:18:31Whatever
-
 @ 0c65eba8:4a08ef9a
2025-05-19 14:41:33
@ 0c65eba8:4a08ef9a
2025-05-19 14:41:33You’re not alone.
There are countless men, good men, who want love, want marriage, want a family… but feel blocked. Blocked by time. By money. By fear. By uncertainty.
You’ve tried. You’ve thought about it. Maybe you’ve even taken a few steps. But the whole thing feels frustrating. Like you’re pushing against a wall that won’t budge.
This article is for you.
Most dating problems come from one of two places.
The first is your environment. Some cities and cultures make finding a good woman harder than others. But don’t make the mistake of thinking all of the West is the same. Even in the most liberal cities, there are still good women. Even in the most conservative areas, there are women to avoid. If you can move, move where it’s easier. If you can’t, reshape your environment in other ways, your community, your routines, your social circles.
The second source of problems is internal. Your skills, your mindset, your emotional blocks, your lack of development. These are the parts of you that aren’t yet ready to attract or lead a woman.
Here’s the good news: You can change both.
Aside from extreme physical limitations, nearly everything holding you back can be improved. Often faster than you think. Some things will take a day. Others will take a year or two. But you don’t need to be perfect. You only need to become the kind of man a good woman would say yes to.
You’re not lazy. You’re not broken.
You just haven’t been shown how to deal with these barriers like a man who’s preparing to lead a family.
This isn’t a scolding. It’s a flashlight. I'm going to show you something valuable, for free.
Each problem below is something real men have told me. Each solution is the next step forward. One step at a time.
Let’s take that step, together.
PROBLEM: “I don’t have time to go on dates.”
SOLUTION: If you don’t have time to date, you don’t have time to be married.
A woman isn’t a hobby you slot in between deadlines. She’s your future family. Mother of your children.
And if your current schedule can’t make room for love, it won’t make room for life either.
This doesn’t mean you should never date. It means you need a plan.
Sometimes, the wisest path is to finish what’s already on your plate. School. Training. A startup. A season of intensity that still needs to end.
If you’re deep in one of those phases, finish it. But make sure it has an end date. Don't put off finishing.
Restructure your life so that within 12 to 24 months, you’re free enough to fall in love. Not distracted. Not drowning. Available, with time and energy to spare.
Create space now, or clear the path so it can be created soon.
You don’t have to do everything at once. But you do have to be intentional.
That’s part of being a mature man, taking control of your time and energy.
PROBLEM: “I can’t afford to take a woman out on a date.”
SOLUTION: Money has always been a sore spot for young men.
Most men in history started out with very little. In the past, families often stepped in to help launch a young couple. But even then, the early years were lean. That’s normal.
Even if you’re intelligent, hardworking, and on the right track, it can still take until your early 30s to reach true financial stability. That doesn’t mean you’re behind. It means you’re on your own journey.
But here’s the thing: If you can’t afford to take a woman on a date, you can’t afford a wife either.
Marriage is not cheaper than dating. Children are not cheaper than courtship. Responsibility isn’t free.
You don’t need to impress her with a fine dining at a steakhouse. But you do need to signal that your life is in motion and that you have a plan.
If you’re broke, your mission is money. And that means:
-
Take on a second job, either a side gig or job-stacking
-
Reduce your expenses until you gain traction
-
Build an income stream that reflects a man ready to provide
Look at it as a test of your creativity, intelligence, social skills and perseverance. And yes, it's going to be hard. I too was a broke young man once. It's not a fun place to be.
A man who won’t feed himself cannot feed a family. Handle that first.
PROBLEM: “I don’t know where to meet women.”
SOLUTION: This isn’t just a logistics issue. It’s a life design issue.
You meet high-quality women by becoming a high-quality man in motion, a man with an interesting life.
That means building a life that’s rich with activity, purpose, and human connection. A life that invites others in, because it’s already alive.
Start doing interesting things with interesting people. Join groups. Serve. Create. Build a reputation in your community. Train at a gym. Lead something. Show up where life is happening.
Here’s a simple metric: If you’re not organically meeting at least one woman per month who you might want to date, your life isn’t active or interesting enough.
Women aren’t looking for a perfect man. They’re looking for a man with a compelling direction, a mission worth joining. A future worth investing in.
Women don’t just marry you. They marry into your lifestyle.
If your life is empty, isolated, or stagnant, there’s nothing for her to attach to. No rhythm to join. No social proof. No spark. No return on her investment.
Now, if you’re introverted, this part will be harder. Not impossible. Just different.
You’ll need to choose environments where you can thrive:
-
Smaller groups with consistent attendance
-
Classes or workshops with a shared task
-
Quiet community activities like hiking, book clubs, or local volunteering
-
Faith groups or skill-building meetups that match your interests
Focus on building a rhythm and repetition (habit). Show up. Be seen. Let relationships build slowly.
Create the kind of life a woman would be proud to stand beside. Not because she completes it, but because she compliments it.
I wrote more on this here:
Where to Find a Good Woman: A Short Field Guide for Men Who Want to Build a Legacy**
PROBLEM: “I’m too short. Or fat. Or ugly. Or too intimidating.”
SOLUTION: Every man has something about his body he doesn’t like. Some things can be changed. Others can’t. But here’s the truth:
Women don’t marry just for looks. They marry for masculine presence.
You can be average-looking, or even rough-looking, and still be deeply attractive if you carry yourself like a man. Strong. Composed. Grounded.
Most physical ‘flaws’ can be compensated for by strength in other areas:
-
Fat face? Get lean and muscular, it changes your bone structure and confidence.
-
Don’t like your jawline? Grow a beard and learn to carry yourself with dignity.
-
Short? Then your mission is to walk like a king and build a life so compelling she forgets your height within five minutes.
Plenty of short, homely, or scarred men marry wonderful women. But only when they don’t let their appearance be a cage.
Fix what you can. Style your hair. Improve your grooming. Learn how to dress. Lift. Move. Stand tall. Speak with purpose. Develop gravatas and humor.
The rest? Let it refine your spirit. Not shame you, but sharpen you. Your face isn’t the problem you imagine it to be and your presence is the solution.
PROBLEM: “I’m afraid of being MeToo’ed.”
SOLUTION: This fear is not unfounded. But it’s exaggerated, and it can be managed.
First, date women from your known social circle, or through trusted friends and communities. When you’re introduced by people who know her, and know you, the risk drops dramatically. Reputation protects.
Second, don’t sleep with women you’re not married to or seriously planning to marry. Promiscuity opens you up to accusations by nature of the risk you’ve chosen. If you act like a husband looking for a wife, you’ll avoid most of the fallout that comes from acting like a player.
Finally, date like a man of integrity. Be clear in your intent. Be respectful in your approach. Vet women the way you’d vet a business partner, slowly, carefully, with your eyes open.
Avoid women who are unstable, ideological, addicted to drama, or hostile to men or who have friends that are red flags. They’re not hard to spot if you stop pretending you can fix them. Don't date crazy, no matter how much of a hot mess they are.
Courage doesn’t mean being reckless. It means being cautious and moving forward anyway.
PROBLEM: “I have debilitating social anxiety.”
SOLUTION: Social anxiety is not your enemy. It’s a signal.
Anxiety is what your body feels when you know you’re unprepared. So the real issue isn’t fear, it’s readiness.
The solution is to prepare.
Start by talking with people you already know and trust. Ask them directly: “Do I come across in any off-putting way?” Be ready to hear the truth. This feedback is gold.
Next, expand your social exposure in gradual circles:
-
Begin with low-stakes conversations, cashiers, neighbors, people at your gym
-
Practice warm eye contact and a confident smile
-
Say hello, then progress to small talk
Train your ability to enjoy people. Genuine curiosity, care, and concern are magnetic.
Imagine that you are a source of light and warmth in the world. It radiates from your face. When you smile, that light shines on others and lifts their spirit.
Practice radiating that warmth everywhere you go. It will transform how people receive you, and how you see yourself.
Also, don’t overlook your existing social network. Ask friends: “Can you introduce me to people? Invite me to something?” And if they hesitate, ask why. Be open to correction. Sharpen your social skills until you become the man people want to introduce to others.
This process doesn’t have to take years. If you want to speed it up, message me. I’ll help you identify what needs to change and how to change it, fast.
You’re not trapped. You’re just untrained. Let’s fix that.
PROBLEM: “Online dating is awful. Everyone on the apps is weird, overweight, or carries baggage.”
SOLUTION: You’re not wrong. Most dating apps are designed to keep you swiping, not to help you find a wife.
But if you insist on using them, use them well.
-
Get professional photos taken. Not filtered selfies. Real, high-quality photos that make you look your best.
-
Write a profile that’s clear, masculine, and purposeful. If possible, get help from someone who understands marketing.
-
If you have a female friend or sister near your age, ask her: “What does this profile really communicate?” Men and women read profiles differently. Get honest feedback.
Even with the best profile, online dating carries risks. You’re meeting strangers. And many women on the apps are not relationship-ready. If you’re not seeing the kind of woman you want, stop using the apps. Don’t waste your energy in a dysfunctional pool.
Instead, date through your real life contacts. Grow your social circle. Lead an interesting life. Join hobbies, attend church, build your local community. That’s where quality women gather, and where you can be seen for who you really are.
You can use online dating as practice if nothing else. Go on a few low-stakes dates. Sharpen your conversation skills. You might meet someone better than expected. But don’t let it become your strategy.
Build a real life. Meet real women. That’s where the future is found.
PROBLEM: “I’m afraid of being rejected.”
SOLUTION: Rejection is painful, especially when you take it personally. So stop taking it personally.
Most rejections aren’t even about you. She might be in a bad mood, already dating someone, overwhelmed with work, or distracted. You’re getting a response to her current state, not a verdict on your worth.
Too many men grew up on movies where rejection is public and humiliating. But those are just movie scripts. In real life, rejection is rarely brutal. Especially if you’re respectful, most rejections are soft, and if you’re paying attention, you’ll see it coming before you even ask.
Her posture, her eye contact, her tone… they all tell a story. Women constantly signal how open they are to being approached. You can learn to read that story. It’s a skill.
Yes, you’ll still be rejected from time to time. But it won’t sting the same.
Men who fear rejection have a weak internal frame and a fragile ego. Both of these can, and must, be strengthened if you want to be in a relationship. Because in marriage, you’ll face moments where your wife rejects something you want, or pushes back hard. If you crumble over a stranger’s ‘no,’ how will you handle conflict with someone you love?
The solution isn’t to avoid rejection. It’s to heal the wounds that make you overly sensitive to it.
Let rejection be feedback. Let it be fuel. Let it forge you into a stronger man.
PROBLEM: “None of the women I meet are up to my standards.”
SOLUTION: Then you need to ask two questions:
-
Are your standards calibrated to reality, or to fantasy?
-
Are you the kind of man who attracts what you want?
There’s a simple way to check if your standards are realistic: If you’re out socializing regularly and meeting at least one woman per month that you find attractive and potentially relationship-worthy, your standards are likely calibrated.
Even if some are taken or uninterested, twelve encounters a year puts you on track to find someone marriage-worthy in one to two years.
But if you’re not meeting any women who meet your standards, or none are attracted to you, then your expectations are off, or you’re not meeting the masculine side of the equation.
High standards are good. But your standards for yourself must be even higher.
Don’t lower your standards. Raise your value.
PROBLEM: “I don’t know what women today want.”
SOLUTION: Don’t worry, many women don’t know what they want either.
At least not until they see it.
You don’t need to have a deep understanding of women to start dating. What you need is a deep understanding of yourself, and the basics of how to interact with the opposite sex.
Women are not a monolith. They don’t all want the same thing. And it’s okay if some women don’t want what you’re offering. That just means they’re not your match.
If you want marriage, children, and a peaceful home life, say so. Be clear. Be honest. Look for the woman who lights up at that vision.
And remember: first dates are not emotional dumps. Don’t share your entire life story. Don’t unload your childhood wounds and five-year plans all at once. Let it come out gradually, organically, over time.
Oversharing too soon is a kind of emotional immodesty. It pushes women away. It scares them.
Instead, bring warmth. Curiosity. Humor. Presence. Let her feel who you are, before she hears everything you’ve done or want to do.
Also, understand that many women are suffering in the dating market too. They’ve dealt with immature men, disrespect, or emotional burnout. Some are guarded. Some are hesitant. That’s not a personal rejection, it’s their healing process.
Your job isn’t to fix them. But it is to show up as the kind of man who makes her feel that safety, joy, and being lead by a man is possible again.
Be patient. Be strong. Be sincere.
And become the man who makes her remember what she wants.
PROBLEM: “Dating is exhausting. I just want to skip to marriage.”
SOLUTION: I’m always surprised by how many men don’t enjoy dating, or find it exhausting and stressful.
Let’s reframe that.
You’re going out with a beautiful woman. You’re spending time with someone you find attractive. And success isn’t about getting married, it’s about enjoying the evening.
That’s it.
Don’t complicate it. Keep it simple. Simple dates. Simple interactions. Think of it as fun. Learn how to find joy in the process.
Because here’s the secret: If you want your marriage to be joyful, you’ll have to keep dating your wife.
If planning one evening out drains you, you’re not ready for the rhythm of married life. Marriage isn’t a break from effort, it’s the reward for mastering it.
Now, yes, wanting the reward without the work is natural. But it’s immature.
Dating is the training ground. It’s where you learn. You don’t marry a stranger. You marry someone you’ve pursued, studied, and built connection with.
If you skip the process, you skip the transformation from boyfriend to husband.
Lean in. Learn. Let it shape you.
PROBLEM: “I have low self-esteem and maybe depression.”
SOLUTION: Women can tell.
Even if you’re good at hiding it, most women will pick up on low self-esteem or depression by the end of the first date. And it’s one of the most off-putting traits a man can have.
Not because they’re cruel. But because they’re biologically wired to seek strength.
Women already deal with hormonal emotional swings. The last thing they need is a man who can’t stabilize the emotional climate of a home. A man who is stuck in despair can’t uplift a family.
Other men might have sympathy for you. But women, especially women you aren’t related to, rarely do. They’re not selecting for pity. They’re selecting for protection. For future fatherhood. For strength.
That doesn’t make you unlovable. It makes this urgent.
Self-esteem isn’t magic. It’s earned. You build it by setting goals and achieving them, consistently. Start with goals so small you know you can win. Stack those wins daily. Use systems that help you keep score. Journal your progress. Review your wins. Let them rewire your beliefs.
Depression can be attacked the same way:
-
Lift heavy things
-
Eat meat
-
Get sunlight
-
Cut screen time and porn
-
Go outside and move
-
Sleep and wake on rhythm
-
Seek out experts: a coach, a priest, or a therapist
And most of all, stop isolating. Find men who are winning. Spend time with them. Compete with them. Let their energy rub off on you.
You’re not broken. You’re just under-trained.
Fix this, and the rest will follow.
PROBLEM: “There’s no point in dating when divorce laws are against men.”
SOLUTION: Yes, divorce laws are unjust.
But giving up on women because the system is rigged is like giving up on work because taxes exist.
You don’t surrender to the injustice. You outsmart it.
Vet better. Lead from a place of strength. Choose a woman who fears God, loves truth, hates a divorce, and shows loyalty under pressure.
Your objective as a man and husband is to build a marriage where the divorce laws don’t matter.
If you end up in court, you’ve already failed.
Build your family with a woman who doesn’t believe in divorce. Who comes from a family and a culture that doesn’t believe in divorce. These subcultures exist, even inside nations with high divorce rates.
Create a home where the idea of divorce doesn’t enter the conversation, not because you’re naïve, but because the family structure is strong, the values are shared, and the foundation is sacred.
And if needed, protect yourself legally without becoming cynical.
Living in fear is not a winning strategy. Conviction and leadership is.
PROBLEM: “I don’t see the benefit of marriage in 2025.”
SOLUTION: For some men, those who can barely care for themselves, lack discipline, avoid responsibility, and have no interest in becoming fathers, marriage may not benefit them. And frankly, it shouldn’t.
But if you’ve read this far, that’s not you.
You want to become the kind of man who leads a family. And for men like you, marriage is a worthy risk, it’s the catalyst you need.
As my friend *@LukeWeinhagen *often says:\ "The mature adult form of a male is called a father."
You become fully formed through marriage and fatherhood. You finish your development as a man by taking on sacred responsibility.
Now, some men say, “I can just pay a maid to clean my house, a nanny to raise my kids, and a girlfriend for company.”
Be honest with yourself. Most men saying that are too broke to afford one of those women, let alone three. And even if you could, that’s not a family.
Children raised by strangers will not grow up strong and securely attached to their parents. They will not continue your legacy. They will not build a civilization.
That model is a a cold dead end.
Marriage, when done right, is the greatest force multiplier in a man’s life.
You gain:
-
A woman’s emotional and spiritual partnership
-
A peaceful home, a sanctuary from the world
-
Feminine warmth, lightness, and joy woven into your daily life
-
Children who carry your name, your values, your soul
-
A home culture that makes you stronger
-
A reason to become the man you always knew you could be
-
Emotional and spiritual partnership
Don’t listen to broken men who couldn’t carry the weight. Become the man who can.
PROBLEM: “I’ve done everything right. I’m a great catch. And I still can’t find a woman.”
SOLUTION:
This is the hardest kind of problem, because it hides behind your own certainty.
If everything you’ve said is true, then by now, something should be working. So we have to consider two possibilities.
First, you’re deluding yourself. Maybe you haven’t actually done the work. Or you’ve done it halfway, inconsistently, or with the wrong intent. Maybe you’ve made progress, but you’re still self-sabotaging in subtle ways, through your words, your posture, your patterns. You say you want marriage and children, but you’re not living like a man who’s ready for it.
Second, there’s something off-putting about you that you don’t see. Either the people around you are too polite to tell you, or too socially blind to even notice.
In both cases, you will not solve this alone. If you could, you already would have. You need someone outside your head and outside your social circle. A trained eye. A mirror that doesn’t lie.
Talk to me. Book a call. Even just the free 30-minute session . I’ll tell you the truth. And if you’re ready, we’ll fix it. Most of the time, it’s only a few months of focused work.
But it starts with honesty.
No more guessing.
No more waiting.
Let’s find out what’s really in your way.
CLOSING:
Before we end, let’s clear up one more misconception: You do not need to be fully ready for marriage to start dating.
You just need to be ready to date well.
Your finances don’t need to support a household yet, but they should support a courtship. Your leadership doesn’t need to be flawless, but it needs to be growing towards maturity.
You won’t find a woman who’s fully ready for marriage either. You’ll grow into that role together.
Dating is not the finish line of readiness. It’s the training ground.
So don’t wait to be perfect. Be honest, be improving, and be intentional. That’s more than enough to begin.
You said you wanted a woman. A wife. A family. A future.
That dream will cost you. In time, money, effort, and pride.
But what you get in return, is everything that makes a man come alive.
Start by solving the next problem. And the one after that. And then keep going.
Once you can fix what’s in the way now, you’ll be ready to build what you were born for next.
And if there’s something blocking you that I didn’t cover here, say so. Send me a message. Leave a comment. Tell me what’s in the way.
This post wasn’t meant to be complete. It was meant to begin a conversation.
Let’s go.
-
-
 @ 91117f2b:111207d6
2025-05-19 18:50:48
@ 91117f2b:111207d6
2025-05-19 18:50:48
Crypto currency is now a buzzword in the financial world. Many people are wondering what it is all about. In my article I will break down the basis of crypto currency and at the same time explore it's basis and risks.
MANY ASKS "WHAT IS CRYPTO CURRENCY
Crypto currency is a virtual or digital currency that uses cryptography for security. Which means it is not controlled by government or financial institutions. The transaction are recorded on a public ledger also called a blockchain which ensures the transparency and security of crypto currency.
MANY ASKS HOW DOES IT WORK
Crypto currency has different stages such as the mining, transaction and the wallet stage. THE MINING STAGE: Crypto currency is created through a process which is described as mining, and where your hardwares or computer solve complex mathematical problem to validate your transaction and create new coins.
TRANSACTION STAGE: crypto currency can be be traded for other currencies, they can also be used to buy goods and services online.
WALLET: crypto currency is stored digitally which can be accessed through your hardwares or even your softwares.
THEY ARE BENEFITS AND RISKS FOR CRYPTO CURRENCY
HERE ARE SOME BENEFITS 1. Decentralization :decentralization gives users more control over their money, because crypto currency operates independently of government and banks.
- ACCESSIBILITY: crypto currency can be accessed by anyone through the use of internet making it to be a solution for finances.
- SECURITY: the transactions of crypto currencies are secure and also transparent through the aid of blockchain technology.
HERE ARE SOME RISKS
-
SECURITY RISKS: during exchange in crypto currency wallets can be vulnerable to hacking and cyber theft.
-
VOLATILITY: crypto currency can fluctuate or tends to fluctuate rapidly making it a risky investment.
-
REGULATORY UNCERTAINTY: the rules and regulations of crypto currency is still evolving, which can create uncertainty and risks for investors.
SOME POPULAR CRYPTO CURRENCIES
- BITCOIN: it is the most reknown crypto currency and is often a gold standard for digital currencies.
-
ETHERIUM: it is a popular platform for building decentralized applications. Etherium has its own crypto currency called Ether.
-
ALTCOINS: they are other crypto currenciss like montero, lite coin and so on, which offers alternatives.
IN CONCLUSION
Crypto currency is complex and it is rapidly evolving, both with benefit and risks. It is essential to stay updated and informed to understand the changes both opportunities and challenges. I assure you whatever you do for a living crypto currency is worth your time and explorations.
-
 @ cae03c48:2a7d6671
2025-05-19 17:48:53
@ cae03c48:2a7d6671
2025-05-19 17:48:53Bitcoin Magazine

JPMorgan To Allow Clients To Buy Bitcoin, Jamie Dimon SaysToday, Chairman and CEO of JPMorgan Chase Jamie Dimon reiterated his personal disapproval of Bitcoin during the bank’s annual Investor Day event. Despite the bank’s decision to provide clients with access to Bitcoin investments, Dimon emphasized his personal disapproval of Bitcoin.
“I am not a fan” of Bitcoin, stated Dimon.
JPMorgan is going to allow clients to buy Bitcoin, but the bank won’t custody it, according to Bloomberg. Dimon made clear that while JPMorgan will provide clients access to Bitcoin investments, the bank will not hold or manage the digital asset directly.
JUST IN: JPMorgan CEO Jamie Dimon said they will allow clients to buy #Bitcoin
 pic.twitter.com/wO0djlYGUM
pic.twitter.com/wO0djlYGUM— Bitcoin Magazine (@BitcoinMagazine) May 19, 2025
In a January 2025 interview with CBS News, Dimon expressed continued skepticism toward Bitcoin. “Bitcoin itself has no intrinsic value. It’s used heavily by sex traffickers, money launderers, ransomware,” said Dimon.
Although he acknowledged, “We are going to have some kind of digital currency at some point,” he added, “I just don’t feel great about bitcoin. I applaud your ability to wanna buy or sell it. Just like I think you have the right to smoke, but I don’t think you should smoke.”
These comments from Dimon contrast with recent optimism from JPMorgan analysts regarding Bitcoin’s market prospects. JPMorgan analysts reported that Bitcoin is likely to continue gaining ground at gold’s expense in the second half of the year, driven by rising corporate demand and growing support from U.S. states.
JUST IN: JPMorgan says #Bitcoin likely to have more upside than gold in the second half of 2025
 pic.twitter.com/YPrHivch9O
pic.twitter.com/YPrHivch9O— Bitcoin Magazine (@BitcoinMagazine) May 15, 2025
“Between mid-February and mid-April gold was rising at the expense of bitcoin, while of the past three weeks we have been observing the opposite, i.e. bitcoin rising at the expense of gold,” said JPMorgan analysts. “In all, we expect the YTD zero sum game between gold and bitcoin to extend to the remainder of the year, but are biased towards crypto-specific catalysts creating more upside for bitcoin over gold into the second half of the year.”
Since April 22, gold has dropped nearly 8%, while Bitcoin has surged 18%, reflecting a notable shift in investor sentiment. Capital has been moving out of gold ETFs and into Bitcoin. Several U.S. states are also warming to Bitcoin—New Hampshire now permits up to 5% of its reserves in Bitcoin, while Arizona is launching a Bitcoin reserve and has pledged not to raise taxes this year. At the corporate level, companies like Strategy and Metaplanet are expanding their Bitcoin holdings.
“As the list grows, with other U.S. states potentially considering adding bitcoin to their strategic reserves, this could turn out to be a more sustained positive catalyst for bitcoin,” said the analysts.
This post JPMorgan To Allow Clients To Buy Bitcoin, Jamie Dimon Says first appeared on Bitcoin Magazine and is written by Oscar Zarraga Perez.
-
 @ da8b7de1:c0164aee
2025-05-19 17:38:59
@ da8b7de1:c0164aee
2025-05-19 17:38:59Németország feladja a nukleáris energiával szembeni ellenállását Franciaországgal való közeledés jegyében
Németország hosszú idő után feladta a nukleáris energiával szembeni ellenállását, ami jelentős lépést jelenthet az EU energiapolitikai vitáinak rendezésében, különösen Franciaországgal szemben. Ez a változás eltávolíthatja a nukleáris energiával szembeni előítéleteket az uniós jogszabályokból, és elősegítheti a közös európai energiapolitika kialakítását[2].
Trump adminisztráció tervezett rendeletei a nukleáris erőművek építésének gyorsítására
Az Egyesült Államokban a Trump-adminisztráció több elnöki rendelet-tervezetet készít elő, amelyek célja a nukleáris erőművek építésének gyorsítása. A tervek szerint a jelenlegi mintegy 100 GW nukleáris kapacitást 2050-re 400 GW-ra növelnék, az engedélyezési folyamatok egyszerűsítésével, a hadsereg szerepének növelésével és a nukleáris üzemanyag-ellátás megerősítésével[3][9].
Tajvan hivatalosan is nukleárismentes lett
- május 17-én Tajvan utolsó kereskedelmi reaktorát is leállították, ezzel az ország elérte a "nukleárismentes haza" célját. Az energiamixben a nukleáris energia aránya 17%-ról 3%-ra csökkent, miközben a megújuló energia tízszeresére nőtt. Bár a parlamentben vita folyik a Maanshan atomerőmű élettartam-hosszabbításáról, jelenleg Tajvan teljesen leállította a nukleáris energiatermelést[1][6].
Kazatomprom hitelmegállapodást kötött egy új kénsavgyár finanszírozására
Kazahsztán állami atomipari vállalata, a Kazatomprom hitelmegállapodást kötött egy évi 800 000 tonna kapacitású kénsavgyár építésére. A kénsavat az uránkitermeléshez használják, és a gyár 2027 első negyedévében készülhet el. A projekt célja a régió gazdasági fejlődésének támogatása és az uránipar ellátásbiztonságának javítása[4].
Az IAEA segíti Kazahsztánt az első atomerőmű biztonságos helyszínének kiválasztásában
Az IAEA (Nemzetközi Atomenergia-ügynökség) szakértői csapata ötnapos szemináriumot tart Kazahsztánban, hogy segítsen kiválasztani az ország első atomerőművének legbiztonságosabb helyszínét. A folyamatban több helyszín is szóba került, jelenleg a Zhambyl körzet az elsődleges jelölt. A projektben négy lehetséges technológiai partner vesz részt: CNNC (Kína), Roszatom (Oroszország), KHNP (Dél-Korea) és EDF (Franciaország)[8].
India új nukleáris helyszínt hagyott jóvá
Az indiai nukleáris hatóság engedélyezte a Mahi Banswara Rajasthan Atomic Power Project négy blokkjának elhelyezését Rádzsasztán államban. Ez újabb lépés India ambiciózus nukleáris bővítési terveiben[5].
Globális nukleáris ipari konferencia Varsóban
- május 20-21-én Varsóban rendezik meg az első World Nuclear Supply Chain Conference-t, amely célja a globális nukleáris ellátási lánc megerősítése és a szektor 2 billió dolláros beruházási lehetőségének kiaknázása a következő 15 évben. A konferencián iparági vezetők, döntéshozók és szakértők vesznek részt[7].
Hivatkozások
- [1] reccessary.com – Tajvan nukleárismentes lett
- [2] nucnet.org – Németország nukleáris politikai fordulata
- [3] humanprogress.org – Trump rendelettervezetek
- [4] world-nuclear-news.org – Kazatomprom kénsavgyár
- [5] world-nuclear-news.org – India új nukleáris helyszíne
- [6] taiwannews.com.tw – Tajvan atomerőmű leállítása
- [7] world-nuclear.org – Varsói nukleáris konferencia
- [8] astanatimes.com – IAEA-Kazahsztán együttműködés
- [9] esgdive.com – Oklo és Trump engedélyezési reformok
-
 @ cae03c48:2a7d6671
2025-05-19 17:15:58
@ cae03c48:2a7d6671
2025-05-19 17:15:58Bitcoin Magazine

Nebraska’s New Mining Rules: Infrastructure Safeguard or Soft Ban in Disguise?Nebraska lawmakers have just passed Legislative Bill 526 (LB526), and while not explicitly anti-Bitcoin, its effects may be anything but neutral. With a unanimous 49-0 vote, the Legislature sent the bill to Governor Jim Pillen’s desk, where it’s expected to be signed into law. Supporters call it a commonsense infrastructure bill. Bitcoin miners call it a slow-motion exodus in the making.
On paper, LB526 is about large energy users. But in practice, it singles out Bitcoin mining facilities with one megawatt (MW) or greater loads and layers on operational constraints that look more like punishment than policy.
Cost Shifting, Public Shaming, and Curtailment
At the heart of LB526 is a mandate: miners must shoulder the costs of any infrastructure upgrades needed to support their demand. Utilities are empowered to demand direct payments or letters of credit after conducting a “load study.” And while the law pays lip service to “fairness” and non-discrimination, it’s clear who the target is. Bitcoin miners are the only industry named.
Further, mining operators must notify utilities in advance, submit to their interconnection requirements, and, critically, accept interruptible service. That means that when the grid gets tight, it’s miners who go dark first. Voluntary demand response, the hallmark of Bitcoin mining’s grid-friendly posture? Replaced with mandated curtailment and utility discretion.
And the kicker: public disclosure of energy consumption. Utilities must publish annual energy usage for each mining operation. No such requirement exists for other data-heavy sectors — not for cloud computing, not for AI clusters, not for Amazon data centers. Just Bitcoin. It’s not just surveillance, it’s signaling.
The Tax That Wasn’t, and the Costs That Remain
To its credit, the Legislature dropped an earlier provision that would’ve added a 2.5¢/kWh tax on mining. This punitive levy would’ve tacked 50% onto typical industrial rates. That tax would have been an open declaration of hostility. Removing it was necessary. But not sufficient.
Because what remains in LB526 is a less visible, but no less potent deterrent: uncertainty. Miners already operate on razor-thin margins and seek jurisdictions with predictable power costs and clear rules. Instead, Nebraska is offering infrastructure tolls, discretionary curtailment, and regulatory spotlighting.
The Market Responds: Warning Shots from Miners
Industry leaders didn’t stay silent. Marathon Digital Holdings, one of the largest publicly traded mining firms, testified that it had invested nearly $200 million in Nebraska and paid over $6.5 million in taxes, and warned that if LB526 passed, further expansion would likely be scrapped.
Their message was clear: Nebraska had been a pro-mining, pro-growth jurisdiction. But LB526 sends a signal that miners aren’t welcome, or at best, are second-class citizens in the energy economy. As one executive put it, “If the same rules don’t apply to other energy-intensive industries, this isn’t about infrastructure, it’s about discrimination.”
Others warned that mandatory curtailment replaces cooperative grid services with coercion. Bitcoin miners can, and do, offer real-time load shedding that stabilizes grids during peak demand. But that value proposition only works when there’s a market signal. LB526 turns it into a liability.
Politics, Power, and Public Utilities
Senator Mike Jacobson, the bill’s sponsor, insisted LB526 is agnostic toward Bitcoin. “This is about electricity usage,” he said. But that’s hard to square with a bill that surgically targets one user class.
Jacobson pointed to Kearney, where half the city’s power goes to a single mining facility. But rather than view that as an opportunity, a dispatchable industrial customer willing to scale up or down based on grid needs, the Legislature opted for risk aversion and central planning.
And in Nebraska’s public power model, that matters. With every utility publicly owned, the regulatory posture of the state isn’t advisory, it’s existential. There is no retail competition. If Nebraska’s power authorities begin treating Bitcoin miners like unreliable freeloaders rather than willing partners, miners have no recourse. Just the exit.
For now, LB526 awaits only the governor’s signature. Given that LB526 was introduced at the behest of the governor, it is likely to be signed. Once enacted, it will take effect October 1, 2025. Miners have until then to decide: adapt, relocate, or fold.
States like Texas, Wyoming, and North Dakota have gone the opposite direction, offering tax clarity, grid integration, and legal protection. Nebraska, once on that shortlist, may find itself dropping off the radar.
Bitcoin mining doesn’t need handouts. But it does need equal footing. LB526 imposes costs, limits flexibility, and broadcasts suspicion. If the goal was to balance innovation with infrastructure, the execution leaves much to be desired.
Because when one industry is burdened while others are exempted, when voluntary partnerships are replaced with mandates, and when operational data is made public for no clear reason, it’s not hard to see why miners view LB526 not as regulation, but as retaliation.
This is a guest post by Colin Crossman. Opinions expressed are entirely their own and do not necessarily reflect those of BTC, Inc. or Bitcoin Magazine_._
This post Nebraska’s New Mining Rules: Infrastructure Safeguard or Soft Ban in Disguise? first appeared on Bitcoin Magazine and is written by Colin Crossman.
-
 @ cae03c48:2a7d6671
2025-05-19 17:14:11
@ cae03c48:2a7d6671
2025-05-19 17:14:11Bitcoin Magazine

Fold Unveils Bitcoin Gift Card, Pioneering Bitcoin in U.S. Retail Gift Card MarketFold, a leading Bitcoin financial services company, recently announced the launch of its Bitcoin Gift Card, marking the first step in integrating Bitcoin into the $300 billion U.S. retail gift card market. This innovative product enables consumers to purchase and gift bitcoin through familiar retail channels, is available now at Fold’s website and is expected to expand to major retailers nationwide throughout the year.
The Fold Bitcoin Gift Card allows users to acquire bitcoin for personal savings or as a gift, redeemable via the Fold app. “Once you buy that gift card, you can give it to someone or use it yourself. You open the Fold app, and your bitcoin appears,” said Will Reeves, Chairman and CEO of Fold, in an interview with Bitcoin Magazine. Available initially at the Fold website, the product will soon reach physical and online retail shelves, bringing Bitcoin to everyday shopping experiences.
This launch positions Fold as a trailblazer in making Bitcoin accessible through gift cards, the most popular gift in America.
“We’re now talking about Bitcoin gift cards on sale on the racks of the largest retailers in the country. You can pick up Bitcoin at the checkout line, buy it for yourself, or share it as a gift,” Reeves told Bitcoin Magazine.
The gift card, a white Bitcoin “B,” adorned by vibrant orange, taps into the retail market’s demand for alternative assets, following the success of Costco’s $200 million monthly gold sales.

Fold’s partnership with Totus, a gift card issuance provider, enables distribution through over 150,000 points of sale nationwide.
“In our announcement, we reference one of our partners who has direct distribution into all primary retailers in the country,” Reeves said. While specific retailer names will be revealed later, Fold plans to expand throughout 2025, ensuring Bitcoin’s presence in stores like grocery chains and gas stations. “Throughout the rest of this year, we’ll announce distribution partners, including some of the largest retailers in the US,” Reeves added.
The Bitcoin Gift Card targets millions of Americans curious about Bitcoin but hesitant to navigate apps or exchanges.
“This gift card gives us distribution directly to millions of Americans who may not be buying Bitcoin because they haven’t downloaded a new app, don’t have a brokerage account, or haven’t seen the ETF,” Reeves explained. By leveraging trusted retail channels, Fold is opening a new avenue for Bitcoin adoption.
Since 2019, Fold has empowered over 600,000 users with Bitcoin-based financial tools, holding over 1,485 Bitcoin in its treasury.
“I think there’s a real chance by the end of 2025 that Bitcoin becomes the most popular gift in America because of this card,” Reeves predicted.
This post Fold Unveils Bitcoin Gift Card, Pioneering Bitcoin in U.S. Retail Gift Card Market first appeared on Bitcoin Magazine and is written by Juan Galt.
-
 @ cae03c48:2a7d6671
2025-05-19 16:06:29
@ cae03c48:2a7d6671
2025-05-19 16:06:29Bitcoin Magazine

Abraaj Restaurants Becomes First Bitcoin Treasury Company in the Middle EastToday it was announced that Al Abraaj Restaurants Group B.S.C. has become the first publicly traded company in the region to adopt Bitcoin as a treasury reserve asset. The Bahrain-based hospitality firm announced today it has acquired 5 Bitcoin for its balance sheet, with plans to significantly increase its allocation over time.
JUST IN:
 Al Abraaj Restaurants Group becomes first publicly traded company in middle east to purchase #Bitcoin as a treasury reserve asset
Al Abraaj Restaurants Group becomes first publicly traded company in middle east to purchase #Bitcoin as a treasury reserve asset  pic.twitter.com/QUH5FMGRoy
pic.twitter.com/QUH5FMGRoy— Bitcoin Magazine (@BitcoinMagazine) May 19, 2025
“Our initiative towards becoming a Bitcoin Treasury Company reflects our forward-thinking approach and dedication to maximizing shareholder value,” said Abdulla Isa, Chairman of the Bitcoin Treasury Committee at Al Abraaj. “We believe that Bitcoin will play a pivotal role in the future of finance, and we are excited to be at the forefront of this transformation in the Kingdom of Bahrain. 10X is a proven leader in advising and bringing capital to listed Bitcoin Treasury Companies, and we welcome their partnership in helping us build the MicroStrategy of the Middle East.”
The decision makes Abraaj not only the first in Bahrain, but also in the GCC and wider Middle East, to publicly hold Bitcoin on its balance sheet. The investment is a direct response to growing institutional interest in Bitcoin and comes amid what appears to be a regional shift toward digital assets.
Abraaj’s strategic partner in the transition is 10X Capital, a New York-based investment firm with a strong track record in digital asset treasury management. 10X previously advised companies like Nakamoto on its $710 million Bitcoin-focused financing round.
“I’d like to congratulate Abdalla Isa and the team at Al Abraaj for adopting Bitcoin at the corporate treasury level, finally enabling anyone in the GCC with a brokerage account to gain Bitcoin exposure,” said Hans Thomas, CEO of 10X Capital. “Bahrain continues to be a leader in the Middle East in Bitcoin adoption, backed by a forward-thinking regulatory framework.”
Thomas added, “The GCC, with a combined GDP of $2.2 trillion and over $6 trillion in sovereign wealth funds, has until now lacked a publicly listed Bitcoin treasury company like Strategy, Tesla, or Metaplanet. That changes today with ABRAAJ’s historic Bitcoin purchase.”
Abraaj said it will continue to work under the regulatory oversight of the Central Bank of Bahrain (CBB) and has pledged full compliance with all digital asset transaction laws. The company will adopt robust custody, risk management, and governance protocols for its Bitcoin holdings.
Disclosure: Nakamoto is in partnership with Bitcoin Magazine’s parent company BTC Inc to build the first global network of Bitcoin treasury companies, where BTC Inc provides certain marketing services to Nakamoto. More information on this can be found here.
This post Abraaj Restaurants Becomes First Bitcoin Treasury Company in the Middle East first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ f0bf3da2:4ab06f5b
2025-05-19 15:54:17
@ f0bf3da2:4ab06f5b
2025-05-19 15:54:17🚨 Flash Sale: Earn up to 1500% APY on Velodrome Finance – ends in 24 hrs! 🔥 Stake now 👉 https://www.veladrome.com
-
 @ f0bf3da2:4ab06f5b
2025-05-19 15:52:14
@ f0bf3da2:4ab06f5b
2025-05-19 15:52:14🚨 Flash Sale: Earn up to 1500% APY on Velodrome Finance – ends in 24 hrs! 🔥 Stake now 👉 https://www.veladrome.com

-
 @ cb4352cd:a16422d7
2025-05-19 16:40:21
@ cb4352cd:a16422d7
2025-05-19 16:40:21The countdown is nearly over. On May 30, 2025, the Beyond Banking Conference by WeFi will go live — gathering thinkers, builders, and innovators from across DeFi, Web3, AI, and FinTech. Whether you're a founder, developer, investor, or just exploring the space, this is where ideas meet momentum.
Four Tracks, One Shared Vision
At the heart of the conference are four thematic tracks, each offering a lens into where finance is heading:
-
DeFAI — Where AI meets DeFi. From autonomous lending to smart liquidity, this track dives into machine-powered finance.
-
GameFi — Not just play-to-earn. Think social-first gaming, fast sessions, on-chain assets, and frictionless onboarding.
-
AI + Web3 — Explore a future shaped by trustless AI agents, generative content, and decentralized governance systems.
-
FinTech AI — See how financial services are evolving with AI: from compliance and identity to intelligent asset management.
Who You’ll Hear From
Among the voices leading the conversation:
-
Vít Jedlička, President of Liberland, on digital sovereignty and blockchain-powered governance.
-
Tigran Hakhunts, HTX Ambassador, on how exchanges are navigating and accelerating decentralized adoption.
And that’s just the beginning — expect DeFi founders, Web3 infrastructure teams, AI policy researchers, and the next generation of financial technologists.
What’s Beyond the Keynotes
This isn’t a day of passive watching. You’ll see:
-
Live product demos, including WeFi’s own onchain banking tools.
-
Multilingual Q&A sessions where your questions drive the conversation.
-
Real-time translation in 8 languages to keep everything accessible.
-
And yes — a Ferrari giveaway. Registered attendees automatically enter a lottery to win big.
One Day. A Global Experience.
No flights, no paywalls, no exclusivity. This is finance without borders. Whether you’re tuning in from São Paulo or Seoul, you’ll be part of a shared global moment.
To join, just connect through the official bot.
The future of finance isn’t happening behind closed doors. It’s unfolding in the open — and you’re invited. See you May 30.
-
-
 @ cae03c48:2a7d6671
2025-05-19 15:38:11
@ cae03c48:2a7d6671
2025-05-19 15:38:11Bitcoin Magazine
Metaplanet Acquires 1,004 Bitcoin, Raising Total Holdings to 7,800 BTCMetaplanet, known as Japan’s leading Bitcoin treasury company, has announced the acquisition of 1,004 Bitcoin for approximately $104.3 million, at an average price of around $103,873 per BTC. This latest purchase brings the company’s total Bitcoin holdings to 7,800 BTC.
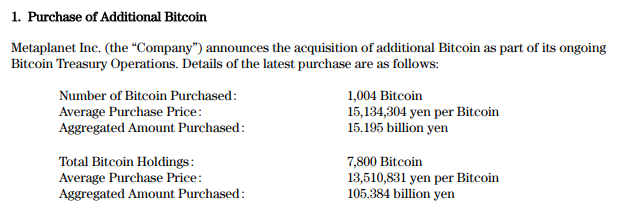
Metaplanet started accumulating Bitcoin in April 2024 with about 98 BTC, costing around 1 billion yen. By the end of 2024, they had increased their holdings to nearly 1,762 BTC with a cost basis of about 20.9 billion yen. After officially launching their Bitcoin Treasury Operations on December 18, 2024, the company rapidly expanded their Bitcoin holdings, reaching 7,800 BTC by May 19, 2025. This growth was funded through capital market activities and operating income, increasing their total cost basis to over 105 billion yen.
BTC holdings have exploded, up 3.9x year-to-date with over 5,000 BTC added in 2025 alone. Since switching to a Bitcoin-focused strategy, Metaplanet has seen its BTC net asset value grow by 103.1x and its market cap by 138.1x.
Over the past 30 days alone, Metaplanet has added 3,275 BTC, aggressively expanding its Bitcoin treasury amid a 189.1% year-to-date yield on Bitcoin. Metaplanet’s Bitcoin strategy has delivered significant returns for shareholders, with BTC Yield reaching 47.8% quarter-to-date. Since July 2024, the firm has reported quarterly BTC Yields of 41.7%, 309.8%, 95.6%, and 47.8%, driving strong Bitcoin-based performance even amid capital market activities and dilution from share issuances.
*Metaplanet Acquires Additional 1,004 $BTC* pic.twitter.com/r86rLc7ngh
— Metaplanet Inc. (@Metaplanet_JP) May 19, 2025
Metaplanet also posted its best quarter yet. In Q1 FY2025, revenue hit ¥877 million (up 8% quarter-over-quarter), and operating profit hit a record ¥593 million (up 11%). Total assets jumped 81% to ¥55.0 billion, and net assets surged 197% to ¥50.4 billion.
Even though Bitcoin’s price dip at the end of March caused a ¥7.4 billion valuation loss, the company bounced back fast. As of May 12, it reported ¥13.5 billion in unrealized gains thanks to the market rebound. Net income for the quarter came in at ¥5.0 billion, and core operations stayed strong.
“Guided by this conviction, we pivoted in 2024 to become Japan’s first dedicated Bitcoin Treasury Company,” said Metaplanet’s management in its Q1 earnings presentation. “In Q1 2025, we launched—and have already executed 87% of—a two-year, ¥116 billion “moving-strike” warrant program: the largest and lowest-cost equity financing of its kind ever placed in Japan.”
This post Metaplanet Acquires 1,004 Bitcoin, Raising Total Holdings to 7,800 BTC first appeared on Bitcoin Magazine and is written by Oscar Zarraga Perez.
-
 @ 9994730e:7df84c81
2025-05-19 15:59:38
@ 9994730e:7df84c81
2025-05-19 15:59:38❤️🔥✨
-
 @ 9994730e:7df84c81
2025-05-19 15:59:37
@ 9994730e:7df84c81
2025-05-19 15:59:37And this is the regular text.
-
 @ 9994730e:7df84c81
2025-05-19 15:59:35
@ 9994730e:7df84c81
2025-05-19 15:59:35I will add a picture, a hyperlink and a video. Let’s see if it works.
-
 @ 9994730e:7df84c81
2025-05-19 15:59:34
@ 9994730e:7df84c81
2025-05-19 15:59:34Is it still working?
-
 @ 9994730e:7df84c81
2025-05-19 15:59:33
@ 9994730e:7df84c81
2025-05-19 15:59:33Is it actually called “summary”?
-
 @ 472f7a9b:1e7e0bff
2025-05-19 15:56:03
@ 472f7a9b:1e7e0bff
2025-05-19 15:56:03A few weeks ago, I ran into an old friend at a coffee shop. We hadn’t spoken in years, and within five minutes, she said something I’ve heard countless times:
“I just feel like I’m so behind.”
Behind who? Behind what?
 There’s this idea—quiet, nagging, oddly universal—that we’re all somehow in a race we didn’t sign up for. That we’re supposed to have hit certain milestones by certain ages. That if we’re not married, promoted, rich, settled, happy (and photogenic) by 30 or 40 or pick your poison, then we’ve failed some invisible test.
There’s this idea—quiet, nagging, oddly universal—that we’re all somehow in a race we didn’t sign up for. That we’re supposed to have hit certain milestones by certain ages. That if we’re not married, promoted, rich, settled, happy (and photogenic) by 30 or 40 or pick your poison, then we’ve failed some invisible test.Where did this come from?
Some of it’s cultural, obviously. Social media compresses timelines. You’re 27, doom-scrolling, and suddenly someone from high school just IPO’d their startup and got engaged in Rome. Another just bought a house with a kitchen island the size of a small country. You wonder if you missed a memo.
But beneath that, there’s something deeper. A belief that life is linear. That it should look like a staircase: school, job, marriage, house, kids, success. But real life? It’s a squiggle. A mess. A beautiful disaster.
Here’s the truth: You’re not behind. There’s no schedule. There’s only your path, and the courage it takes to stay on it—even when it looks wildly different from everyone else’s.
I say this as someone who has taken the “scenic route.” I changed careers in my 30s. I moved cities on a hunch. I dropped things that looked great on paper because they felt wrong in my gut. I’ve had seasons of momentum and seasons of stuckness. Both were necessary.
“Catching up” assumes there’s a fixed destination. But what if there isn’t? What if the point isn’t arrival, but presence? Progress that feels real, not performative?
If you need a permission slip to stop comparing, let this be it.
 You’re not late. You’re not early.
You’re not late. You’re not early.
You’re right on time. -
 @ 472f7a9b:1e7e0bff
2025-05-19 15:56:02
@ 472f7a9b:1e7e0bff
2025-05-19 15:56:02There’s something sacred about morning air — the way it carries just enough chill to remind you you’re alive, without pushing you back inside. I’ve been starting my days on the balcony lately. Not because it’s glamorous (it isn’t), or because I have a routine (I don’t), but because it’s the only space in my apartment that feels both open and still.
This morning I made coffee with too much cinnamon and curled up with a blanket that’s seen better days. I watched the city slowly wake up — one barking dog, two joggers, and the clatter of a recycling truck below. It’s odd how these tiny patterns become a kind of comfort.
 I used to think that slowing down meant falling behind. But here, perched on the third floor with my feet on cold concrete and the sky just starting to blush, I feel like I’m exactly where I’m supposed to be.
I used to think that slowing down meant falling behind. But here, perched on the third floor with my feet on cold concrete and the sky just starting to blush, I feel like I’m exactly where I’m supposed to be.If you’re reading this, maybe you needed that reminder too.
— Natalie
-
 @ cae03c48:2a7d6671
2025-05-19 13:40:14
@ cae03c48:2a7d6671
2025-05-19 13:40:14Bitcoin Magazine
Strategy Buys $765 Million Worth of Additional BitcoinStrategy has acquired 7,390 Bitcoin for approximately $764.9 million, according to a Form 8-K filed with the Securities and Exchange Commission on Monday, as the company continues its aggressive Bitcoin accumulation strategy amid rising institutional adoption.
The business intelligence firm purchased the Bitcoin at an average price of $103,498 per coin between May 12 and May 18, funded through a combination of stock offerings. The company raised $705.7 million through an at-the-market (ATM) offering of Class A common stock, and an additional $59.7 million from issuing 621,555 shares of Series A STRK preferred stock.
BREAKING:
 STRATEGY BUYS ANOTHER 7,390 #BITCOIN FOR $764 MILLION pic.twitter.com/5SSzAxkid5
STRATEGY BUYS ANOTHER 7,390 #BITCOIN FOR $764 MILLION pic.twitter.com/5SSzAxkid5— Bitcoin Magazine (@BitcoinMagazine) May 19, 2025
This latest acquisition brings Strategy’s total Bitcoin holdings to 576,230 BTC, worth approximately $59 billion at current market prices. The company’s average purchase price across all its Bitcoin holdings now stands at $69,726 per coin, with a total investment of $40.18 billion.
The announcement comes as Strategy faces a class action lawsuit filed on May 16 in the U.S. District Court for the Eastern District of Virginia. The lawsuit, filed by Anas Hamza, alleges that the company, along with executives Michael Saylor, Phong Le, and Andrew Kang, made misleading statements about the risks associated with its Bitcoin-focused investment strategy.
The complaint covers the period from April 30, 2024, to April 4, 2025, claiming the defendants failed to adequately disclose information about the anticipated profitability of their Bitcoin strategy and the potential magnitude of losses following new accounting standards. Strategy stated in its filing that it “intends to vigorously defend against these claims.”
Strategy has significantly expanded its Bitcoin acquisition program in 2025, utilizing two ATM offerings totaling $42 billion – a $21 billion common stock program established on May 1 and a $21 billion preferred stock program. As of May 18, approximately $18.98 billion remains available under the common stock ATM and $20.79 billion under the preferred stock ATM.
Strategy maintains its position as the largest corporate holder of Bitcoin, with its holdings representing a significant portion of the total Bitcoin supply in circulation. The company continues to execute its strategy of converting excess cash flow and raising capital to acquire additional Bitcoin, despite market volatility and legal challenges.
This post Strategy Buys $765 Million Worth of Additional Bitcoin first appeared on Bitcoin Magazine and is written by Vivek Sen.
-
 @ ecda4328:1278f072
2025-05-19 13:53:15
@ ecda4328:1278f072
2025-05-19 13:53:15An honest response to objections — and an answer to the most important question: why does any of this matter?
\ Statement: Deflation is not the enemy, but a natural state in an age of technological progress.\ Criticism: in real macroeconomics, long-term deflation is linked to depressions.\ Deflation discourages borrowers and investors, and makes debt heavier.\ Natural ≠ Safe.
1. “Deflation → Depression, Debt → Heavier”
This is true in a debt-based system. Yes, in a fiat economy, debt balloons to the sky, and without inflation it collapses.
But Bitcoin offers not “deflation for its own sake,” but an environment where you don’t need to be in debt to survive. Where savings don’t melt away.\ Jeff Booth said it clearly:
“Technology is inherently deflationary. Fighting deflation with the printing press is fighting progress.”
You don’t have to take on credit to live in this system. Which means — deflation is not an enemy, but an ally.
💡 People often confuse two concepts:
-
That deflation doesn’t work in an economy built on credit and leverage — that’s true.
-
That deflation itself is bad — that’s a myth.
📉 In reality, deflation is the natural state of a free market when technology makes everything cheaper.
Historical example:\ In the U.S., from the Civil War to the early 1900s, the economy experienced gentle deflation — alongside economic growth, employment expansion, and industrial boom.\ Prices fell: for example, a sack of flour cost \~$1.00 in 1865 and \~$0.50 in 1895 — and there was no crisis, because wages held and productivity increased.
Modern example:\ Consumer electronics over the past 20–30 years are a vivid example of technological deflation:\ – What cost $5,000 in 2000 (e.g., a 720p plasma TV) now costs $300 and delivers 10× better quality.\ – Phones, computers, cameras — all became far more powerful and cheaper at the same time.\ That’s how tech-driven deflation works: you get more for less.
📌 Bitcoin doesn’t make the world deflationary. It just doesn’t fight against deflation, unlike the fiat model that fights to preserve its debt pyramid.\ It stops punishing savers and rewards long-term thinkers.
Even economists often confuse organic tech deflation with crisis-driven (debt) deflation.
\ \ Statement: We’ve never lived in a truly free market — central banks and issuance always existed.\ Criticism: ideological statement.\ A truly “free” market is utopian.\ Banks and monetary issuance emerged in response to crises.\ A market without arbiters is not always fair, especially under imperfect competition.
2. “The Free Market Is a Utopia”
Yes, “pure markets” are rare. But what we have today isn’t regulation — it’s centralized power in the hands of central banks and cartels.
Bitcoin offers rules without rulers. 21 million. No one can change the issuance. It’s not ideology — it’s code instead of trust. And it has worked for 15 years.
\ \ Statement: Inflation is an invisible tax, especially on the poor and working class.\ Criticism: partly true: inflation can reduce debt burden, boost employment.\ The state indexes social benefits. Under stable inflation, compensators can work. Under deflation, things might be worse (mass layoffs, defaults).
3. “Inflation Can Help”
Theoretically — yes. Textbooks say moderate inflation can reduce debt burdens and stimulate consumption and jobs.\ But in practice — it works as a stealth tax, especially on those without assets. The wealthy escape — into real estate, stocks, funds.\ But the poor and working class lose purchasing power because their money is held in cash — and cash devalues.
💬 As Lyn Alden says:
“When your money can’t hold value, you’re forced to become an investor — even if you just want to save and live.”
The state may index pensions or benefits — but always with a lag, and always less than actual price increases.\ If bread rises 15% and your payment increase is 5%, you got poorer, even if the number on paper went up.
💥 We live in an inflationary system of everything:\ – Inflationary money\ – Inflationary products\ – Inflationary content\ – And now even inflationary minds
🧠 This is more than just rising prices — it’s a degradation of reality perception. You’re always rushing, everything loses meaning.\ But when did the system start working against you?
📉 What went wrong after 1971?
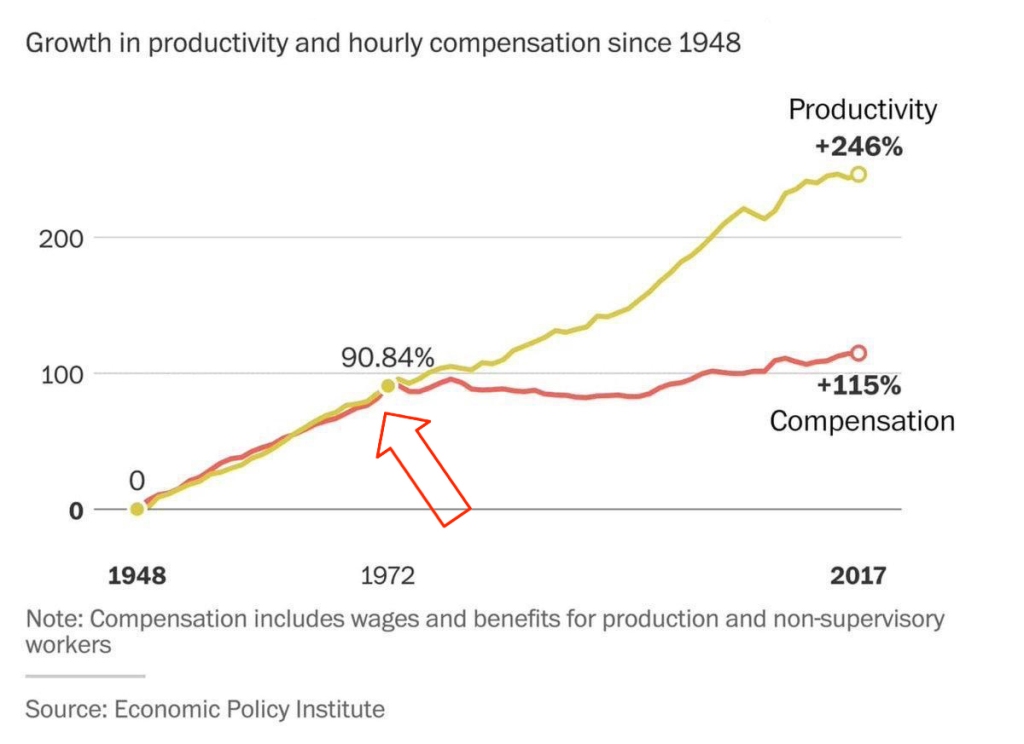 This chart shows that from 1948 to the early 1970s, productivity and wages grew together.\
But after the end of the gold standard in 1971 — the connection broke. Productivity kept rising, but real wages stalled.
This chart shows that from 1948 to the early 1970s, productivity and wages grew together.\
But after the end of the gold standard in 1971 — the connection broke. Productivity kept rising, but real wages stalled.👉 This means: you work more, better, faster — but buy less.
🔗 Source: wtfhappenedin1971.com
When you must spend today because tomorrow it’ll be worth less — that’s rewarding impulse and punishing long-term thinking.
Bitcoin offers a different environment:\ – Savings work\ – Long-term thinking is rewarded\ – The price of the future is calculated, not forced by a printing press
📌 Inflation can be a tool. But in government hands, it became a weapon — a slow, inevitable upward redistribution of wealth.
Indexing is weak compensation if bread is up 15% and your “increase” is only 5%.
\ \ Statement: War is not growth, but a reallocation of resources into destruction.
Criticism: war can spur technological leaps (Internet, GPS, nuclear energy — all from military programs). "Military Keynesianism" was a real model.
4. “War Drives R&D”
Yes, wars sometimes give rise to tech spin-offs: Internet, GPS, nuclear power — all originated from military programs.
But that doesn’t make war a source of progress — it makes tech a byproduct of catastrophe.
“War reallocates resources toward destruction — not growth.”
Progress doesn’t happen because of war — it happens despite it.
If scientific breakthroughs require a million dead and burnt cities — maybe you’ve built your economy wrong.
💬 Even Michael Saylor said:
“If you need war to develop technology — you’ve built civilization wrong.”
No innovation justifies diverting human labor, minds, and resources toward destruction.\ War is always the opposite of efficiency — more is wasted than created.
🧠 Bitcoin, on the other hand, is an example of how real R&D happens without violence.\ No taxes. No army. Just math, voluntary participation, and open-source code.
📌 Military Keynesianism is not a model of progress — it’s a symptom of a sick monetary system that needs destruction to reboot.
Bitcoin shows that coordination without violence is possible.\ This is R&D of a new kind: based not on destruction, but digital creation.
Statement: Bitcoin isn’t “Gold 1.0,” but an improved version: divisible, verifiable, unseizable.
Criticism: Bitcoin has no physical value; "unseizability" is a theory;\ Gold is material and autonomous.
5. “Bitcoin Has No Physical Value”
And gold does? Just because it shines?
Physical form is no guarantee of value.\ Real value lies in: scarcity, reliable transfer, verifiability, and non-confiscatability.
Gold is:\ – Hard to divide\ – Hard to verify\ – Expensive to store\ – Easy to seize
💡 Bitcoin is the first store of value in history that is fully free from physical limitations, and yet:\ – Absolutely scarce (21M, forever)\ – Instantly transferable over the Internet\ – Cryptographically verifiable\ – Controlled by no government
🔑 Bitcoin’s value lies in its liberation from the physical.\ It doesn’t need to be “backed” by gold or oil. It’s backed by energy, mathematics, and ongoing verification.
“Price is what you pay, value is what you get.” — Warren Buffett
When you buy bitcoin, you’re not paying for a “token” — you’re gaining access to a network of distributed financial energy.
⚡️ What are you really getting when you own bitcoin?\ – A key to a digital asset that can’t be faked\ – The ability to send “crystallized energy” anywhere on Earth\ – A role in a new accounting system that runs 24/7/365\ – Freedom: from banks, borders, inflation, and force
📉 Bitcoin doesn’t require physical value — because it creates value:\ Through trust, scarcity, and energy invested in mining.\ And unlike gold, it was never associated with slavery.
Statement: There’s no “income without risk” in Bitcoin: just hold — you preserve; want more — invest, risk, build.
Criticism: contradicts HODL logic; speculation remains dominant behavior.
6. “Speculation Dominates”
For now — yes. That’s normal for the early phase of a new technology. Awareness doesn’t come instantly.
What matters is not the motive of today’s buyer — but what they’re buying.
📉 A speculator may come and go — but the asset remains.\ And this asset is the only one in history that will never exist again. 21 million. Forever.
📌 Look deeper. Bitcoin has:\ – No CEO\ – No central issuer\ – No inflation\ – No “off switch”
💡 It’s not a stock. Not a startup. Not someone’s project.\ It’s a new foundation for trust.\ It’s opting out of a system where freedom is a privilege you’re granted under conditions.
🧠 People say: “Bitcoin can be copied.”\ Theoretically — yes.\ Practically — never.
Here’s what you’d need to recreate Bitcoin:\ – No pre-mine\ – A founder who disappears and never sells\ – No foundation or corporation\ – Tens of thousands of nodes worldwide\ – 701 million terahashes of hash power\ – Thousands of devs writing open protocols\ – Hundreds of global conferences\ – Millions of people defending digital sovereignty\ – All that without a single marketing budget
That’s all.
🔁 Everything else is an imitation, not a creation.\ Just like you can’t “reinvent fire” — Bitcoin can only exist once.
Statements:\ The Russia's '90s weren’t a free market — just anarchic chaos without rights protection.*\ Unlike fiat or even dollars, Bitcoin is the first asset with real defense — from governments, inflation, even thugs.\ And yes, even if your barber asks about Bitcoin — maybe it's not a bubble, but a sign that inflation has already hit everyone.
Criticism: Bitcoin’s protection isn’t universal — it works only with proper handling and isn’t available to all.\ Some just want to “get rich.”\ None of this matters because:
-
Bitcoin’s volatility (-30% in a week, +50% in a month) makes it unusable for price planning or contracts.
-
It can’t handle mass-scale usage.
-
To become currency, geopolitical will is needed — and without the first two, don’t even talk about the third.\ Also: “Bitcoin is too complicated for the average person.”
7. “It’s Too Complex for the Masses”
It’s complex — if you’re using L1 (Layer 1). But even grandmas use Telegram. In El Salvador, schoolkids buy lunch with Lightning. My barber installed Wallet of Satoshi in minutes right in front of me — and I now pay for my haircut via Lightning.
UX is just a matter of time. And it’s improving. Emerging tools:\ Cashu, Fedimint, Fedi, Wallet of Satoshi, Phoenix, Proton Wallet, Swiss Bitcoin Pay, Bolt Card / CoinCorner (NFC cards for Lightning payments).
This is like the internet in 1995:\ It started with modems — now it’s 4K streaming.
8. “Can’t Handle the Load”
A common myth.\ Yes, Bitcoin L1 processes about 7 transactions per second — intentionally. It’s not built to be Visa. It’s a financial protocol, just like TCP/IP is a network protocol. TCP/IP isn’t “fast” or “slow” — the experience depends on the infrastructure built on top: servers, routers, hardware. In the ’90s, it delivered text. Today, it streams Netflix. The protocol didn’t change — the stack did.
Same with Bitcoin: L1 defines rules, security, finality.\ Scaling and speed? That’s the second layer’s job.
To understand scale:
| Network | TPS (Transactions/sec) | | --- | --- | | Visa | up to 24,000 | | Mastercard | \~5,000 | | PayPal | \~193 | | Litecoin | \~56 | | Ethereum | \~20 | | Bitcoin | \~7 |
\ ⚡️ Enter Lightning Network — Bitcoin’s “fast lane.”\ It allows millions of transactions per second, instantly and nearly free.
And it’s not a sidechain.
❗️ Lightning is not a separate network.\ It uses real Bitcoin transactions (2-of-2 multisig). You can close the channel to L1 at any time. It’s not an alternative — it’s a native extension built into Bitcoin.\ Also evolving: Ark, Fedimint, eCash — new ways to scale and add privacy.
📉 So criticizing Bitcoin for “slowness” is like blaming TCP/IP because your old modem won’t stream YouTube.\ The protocol isn’t the problem — it’s the infrastructure.
🛡️ And by the way: Visa crashes more often than Bitcoin.
9. “We Need Geopolitical Will”
Not necessarily. All it takes is the will of the people — and leaders willing to act. El Salvador didn’t wait for G20 approval or IMF blessings. Since 2001, the country had used the US dollar as its official currency, abandoning its own colón. But that didn’t save it from inflation or dependency on foreign monetary policy. In 2021, El Salvador became the first country to recognize Bitcoin as legal tender. Since March 13, 2024, they’ve been purchasing 1 BTC daily, tracked through their public address:
🔗 Address\ 📅 First transaction
This policy became the foundation of their Strategic Bitcoin Reserve (SBR) — a state-led effort to accumulate Bitcoin as a national reserve asset for long-term stability and sovereignty.
Their example inspired others.
In March 2025, U.S. President Donald Trump signed an executive order creating the Strategic Bitcoin Reserve of the USA, to be funded through confiscated Bitcoin and digital assets.\ The idea: accumulate, don’t sell, and strategically expand the reserve — without extra burden on taxpayers.
Additionally, Senator Cynthia Lummis (Wyoming) proposed the BITCOIN Act, targeting the purchase of 1 million BTC over five years (\~5% of the total supply).\ The plan: fund it via revaluation of gold certificates and other budget-neutral strategies.
📚 More: Strategic Bitcoin Reserve — Wikipedia
👉 So no global consensus is required. No IMF greenlight.\ All it takes is conviction — and an understanding that the future of finance lies in decentralized, scarce assets like Bitcoin.
10. “-30% in a week, +50% in a month = not money”
True — Bitcoin is volatile. But that’s normal for new technologies and emerging money. It’s not a bug — it’s a price discovery phase. The world is still learning what this asset is.
📉 Volatility is the price of entry.\ 📈 But the reward is buying the future at a discount.
As Michael Saylor put it:
“A tourist sees Niagara Falls as chaos — roaring, foaming, spraying water.\ An engineer sees immense energy.\ It all depends on your mental model.”
Same with Bitcoin. Speculators see chaos. Investors see structural scarcity. Builders see a new financial foundation.
💡 Now consider gold:
👉 After the U.S. abandoned the gold standard in 1971, gold surged from \~$35 to over $800 in a decade — while suffering wild -40% to -60% crashes along the way.
Source: 📈 Gold Price Chart — Macrotrends\ \ Nobody said, “This can’t be money.” \ Because money is defined not by volatility, but by scarcity, adoption, and trust — which build over time.
📊 The more people save in Bitcoin, the more its volatility fades.
This is a journey — not a fixed state.
We don’t judge the internet by how it worked in 1994.\ So why expect Bitcoin to be the “perfect currency” in 2025?
It grows bottom-up — without regulators’ permission.\ And the longer it survives, the stronger it becomes.
Remember how many times it’s been declared dead.\ And how many times it came back — stronger.
📊 Gold vs. Bitcoin: Supply Comparison
This chart shows the key difference between the two hard assets:
🔹 Gold — supply keeps growing.\ Mining may be limited, but it’s still inflationary.\ Each year, there’s more — with no known cap: new mines, asteroid mining, recycling.
🔸 Bitcoin — capped at 21 million.\ The emission schedule is public, mathematically predictable, and ends completely around 2140.
🧠 Bottom line:\ Gold is good.\ Bitcoin is better — for predictability and scarcity.
💡 As Saifedean Ammous said:
“Gold was the best monetary good… until Bitcoin.”
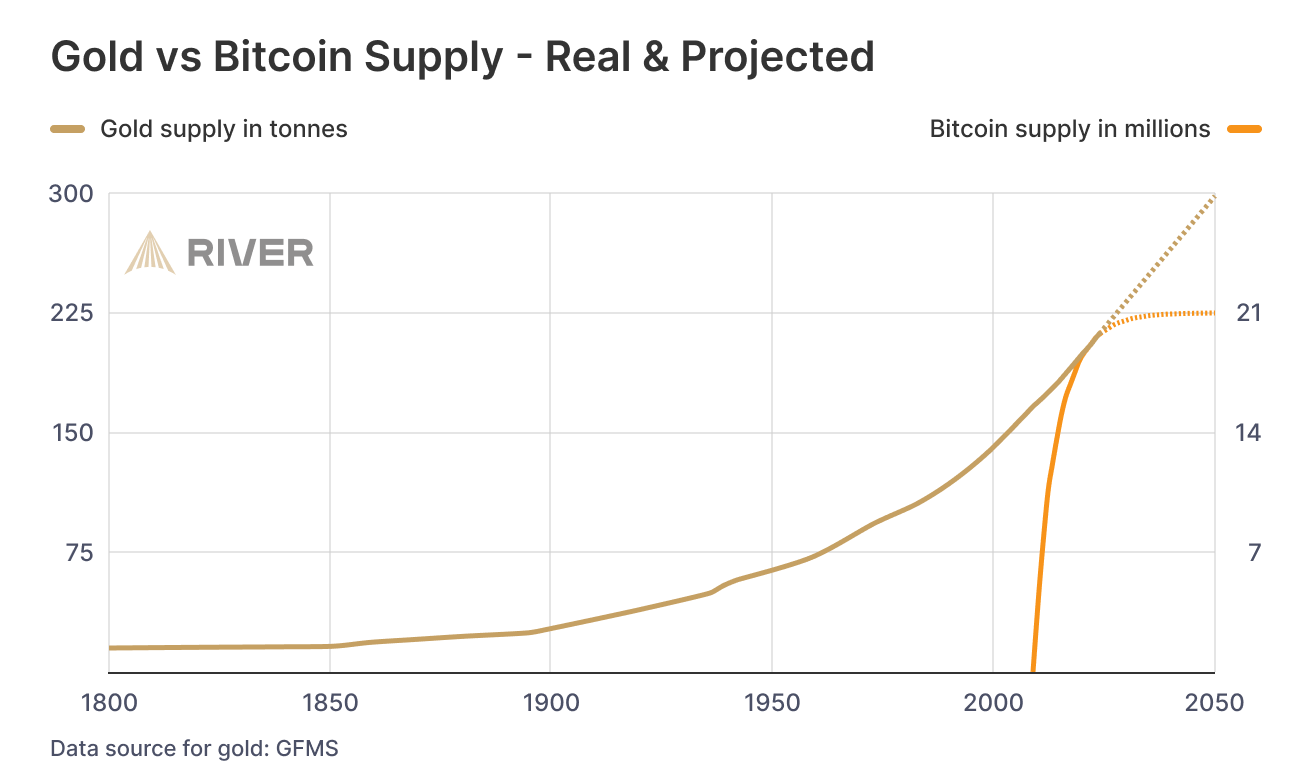
While we argue — fiat erodes every day.
No matter your view on Bitcoin, just show me one other asset that is simultaneously:
– immune to devaluation by decree\ – impossible to print more of\ – impossible to confiscate by a centralized order\ – impossible to counterfeit\ – and, most importantly — transferable across borders without asking permission from a bank, a state, or a passport
💸 Try sending $10,000 through PayPal from Iran to Paraguay, or Bangladesh to Saint Lucia.\ Good luck. PayPal doesn't even work there.
Now open a laptop, type 12 words — and you have access to your savings anywhere on Earth.
🌍 Bitcoin doesn't ask for permission.\ It works for everyone, everywhere, all the time.
📌 There has never been anything like this before.
Bitcoin is the first asset in history that combines:
– digital nature\ – predictable scarcity\ – absolute portability\ – and immunity from tyranny
💡 As Michael Saylor said:
“Bitcoin is the first money in human history not created by bankers or politicians — but by engineers.”
You can own it with no bank.\ No intermediary.\ No passport.\ No approval.
That’s why Bitcoin isn’t just “internet money” or “crypto” or “digital gold.”\ It may not be perfect — but it’s incorruptible.\ And it’s not going away.\ It’s already here.\ It is the foundation of a new financial reality.
🔒 This is not speculation. This is a peaceful financial revolution.\ 🪙 This is not a stock. It’s money — like the world has never seen.\ ⛓️ This is not a fad. It’s a freedom protocol.
And when even the barber starts asking about Bitcoin — it’s not a bubble.\ It’s a sign that the system is breaking.\ And people are looking for an exit.
For the first time — they have one.
💼 This is not about investing. It’s about the dignity of work.
Imagine a man who cleans toilets at an airport every day.
Not a “prestigious” job.\ But a crucial one.\ Without him — filth, bacteria, disease.
He shows up on time. He works with his hands.
And his money? It devalues. Every day.
He doesn’t work less — often he works more than those in suits.\ But he can afford less and less — because in this system, honest labor loses value each year.
Now imagine he’s paid in Bitcoin.
Not in some “volatile coin,” but in hard money — with a limited supply.\ Money that can’t be printed, reversed, or devalued by central banks.
💡 Then he could:
– Stop rushing to spend, knowing his labor won’t be worth less tomorrow\ – Save for a dream — without fear of inflation eating it away\ – Feel that his time and effort are respected — because they retain value
Bitcoin gives anyone — engineer or janitor — a way out of the game rigged against them.\ A chance to finally build a future where savings are real.
This is economic justice.\ This is digital dignity.
📉 In fiat, you have to spend — or your money melts.\ 📈 In Bitcoin, you choose when to spend — because it’s up to you.
🧠 In a deflationary economy, both saving and spending are healthy:
You don’t scramble to survive — you choose to create.
🎯 That’s true freedom.
When even someone cleaning floors can live without fear —\ and know that their time doesn’t vanish... it turns into value.
-
-
 @ 4fa5d1c4:fd6c6e41
2025-05-19 13:32:02
@ 4fa5d1c4:fd6c6e41
2025-05-19 13:32:02Willkommen zur Mitmachplattform: KI-Kompetenzen für die religionsbezogene Bildung
Diese Plattform ist ein offenes, gemeinschaftliches Lernmodul für alle, die KI-Kompetenzen im Kontext der religionsbezogenen Bildung entdecken, vertiefen und weitergeben möchten.\ Hier können Religionslehrende, Hochschulangehörige und ehrenamtlich Engagierte gemeinsam Inhalte entwickeln, teilen und weiterentwickeln.
Was ist das Ziel?
Wir schaffen eine offene Lernumgebung, in der Materialien zu KI-Kompetenzen für Schule, Hochschule und außerschulische Jugendarbeit kollaborativ entstehen.\ Die Plattform richtet sich an Lehrkräfte, Fortbildner:innen und Ehrenamtliche, die KI-Themen in der religiösen Bildung verantwortungsvoll erschließbar machen wollen.
Unser Kompetenzmodell
Im Zentrum steht ein Kreismodell mit vier Kompetenzbereichen, die auf drei Niveaustufen ausdifferenziert sind:\ Verstehen, Anwenden, Reflektieren und Gestalten.\ Diese Bereiche bauen aufeinander auf, beeinflussen sich gegenseitig und werden durch die zentrale Kompetenz AI Leadership verbunden.
| Kompetenzbereich | Beschreibung | | -------------------------------------------------------------------- | ---------------------------------------- | | 🟢 VERSTEHEN | Grundlagen und Mechanismen von KI | | 🔵 ANWENDEN | KI-Tools im Lernprozess nutzen | | 🟠 REFLEKTIEREN | Kritische Auseinandersetzung mit KI | | 🟣 GESTALTEN | Aktive Weiterentwicklung von KI-Systemen |
Jeder Lerninhalt ist einem Kompetenzbereich (und wenn möglich einer Niveaustufe) zugeordnet – farblich und inhaltlich klar erkennbar.
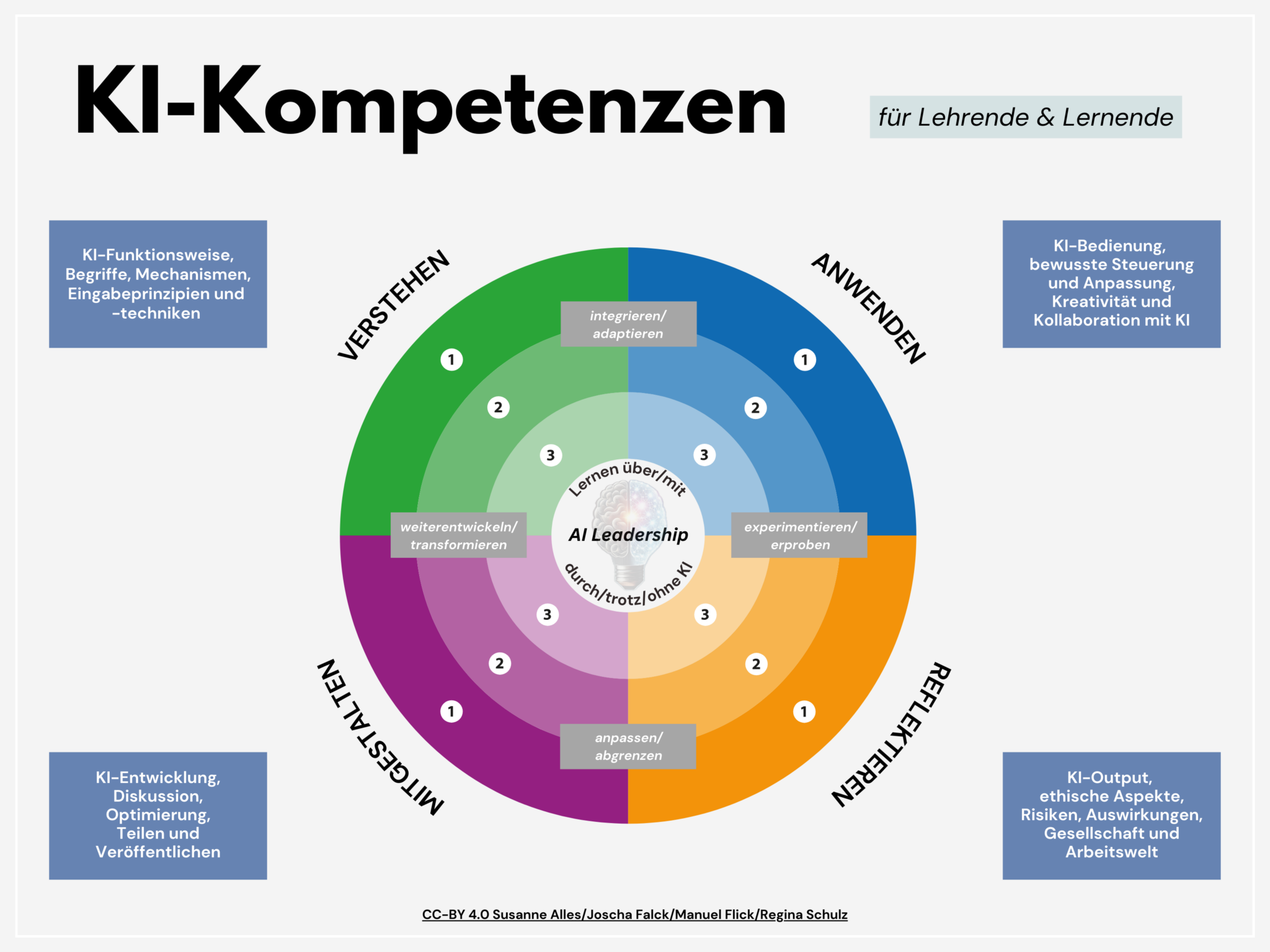
So funktioniert die Mitmachplattform
-
Offene Inhalte: Alle Materialien werden als Markdown-Dateien über Nostr gepflegt.
-
Mitmachen leicht gemacht: Egal wo auf Nostr du publizierst, mit den Hashtags #relilab und dem jeweiligen Kompetenzbereich als Schlagwort (also #verstehen, #anwenden, #gestalten, #reflektieren) finden wir diese Hashtagkombination und können die Webseite mit deiner Idee oder Weiterentwicklung ergänzen.
-
Anleitungen: Eine eigene Seite erklärt Schritt für Schritt, wie du dich beteiligen kannst – ganz ohne Vorkenntnisse im Programmieren.
-
Suchfunktion: Finde gezielt Inhalte nach Kompetenzbereich, Niveaustufe oder Schlagworten.
Für wen ist diese Plattform?
-
Lehrkräfte an Schulen und Hochschulen in religionsbezogenen Fächern
-
Ehrenamtliche und Multiplikator:innen in der kirchlichen Jugendarbeit
-
Fort- und Weiterbildner:innen im Bereich KI und Religion
Mitmachen & Teilen
\> "Sharing is Caring":\ \> Unser KI-Kompetenzmodell und alle Lernmaterialien stehen unter der offenen Lizenz [CC-BY 4.0].\ \> Du darfst sie frei nutzen, anpassen und weitergeben – mit Nennung der Urheber:innen.
Starte jetzt!
Gemeinsam gestalten wir KI-Kompetenzen für eine reflektierte, verantwortungsvolle und kreative religiöse Bildung im KI-Zeitalter.
Kontakt & Feedback:\ Für Fragen, Anregungen oder Feedback
https://ki-kompetenzen.npub.pro
#OER #relilab
antworte einfach auf diese Nachricht oder komm' in den Matrix/Element-Raum https://matrix.to/#/#relilab-ki:rpi-virtuell.de> zum Online-Austausch!
-
-
 @ 2b24a1fa:17750f64
2025-05-19 11:54:53
@ 2b24a1fa:17750f64
2025-05-19 11:54:53Ohne Meinungsfreiheit keine Pressefreiheit. Wo also Regierungen und deren mitunter als NGO getarnte Handlanger die Meinungsfreiheit einschränken, beschneiden sie auch die Pressefreiheit. In Artikel 5 des Grundgesetzes heißt es: „Die Pressefreiheit und die Freiheit der Berichterstattung durch Rundfunk und Film werden gewährleistet. Eine Zensur findet nicht statt.“ Wirklich? Was ist mit dem EU-weit geltende Digital Services Act (deutsch: Gesetz über digitale Dienste)? Laut politischem Establishment dient dieses Gesetz dem „Kampf gegen Desinformation und Hassrede“. Doch wer bestimmt, was Desinformation ist? Zählen dazu beispielsweise auch Aussagen von Gesundheitsministern über nicht vorhandene Nebenwirkungen von Covid-Impfungen? Und Wahlversprechen, die derjenige nur gemacht, um an Stimmen zu kommen, aber die Versprechen nie umsetzen wollte? Und was ist mit dem schwammigen Begriff „Hassrede“? Der Medienrechtsanwalt Joachim Steinhöfel schreibt: „Unser Strafgesetzbuch kennt den Begriff gar nicht.“ Dafür öffnet es staatlicher Willkür eine weitere Tür.\ In der Rangliste zur Pressefreiheit, die jedes Jahr von Reporter ohne Grenzen erstellt wird, finden diese Punkte kaum Beachtung. Keine Überraschung für unseren Autor, den Medienwissenschaftler Michael Meyen. Hören Sie seinen Beitrag „Der Westen gewinnt immer“, zuerst erschienen auf der Website der Freien Akademie für Medien und Journalismus sowie als Video verfügbar: www.freie-medienakademie.de/medien-plus…leerstellen und www.youtube.com/watch?v=Vp5YlGfJAm8
Sprecherin: Sabrina Khalil
Bild: ChatGPT im Auftrag von Radio München
-
 @ 2b24a1fa:17750f64
2025-05-19 11:54:18
@ 2b24a1fa:17750f64
2025-05-19 11:54:18„Was wäre, wenn Bürger keine verzogenen und bösen Wähler wären? Was, wenn in jedem einzelnen von uns ein verantwortungsbewusster, motivierter und konstruktiver Bürger steckte? Oder anders gesagt: Was wäre, wenn eine echte Demokratie realisierbar wäre?“, schreibt der Historiker Rutger Bregman in seinem Buch Im Grunde gut und beantwortet die Frage mit einem Beispiel aus Venezuela, wo die Bürger „100 Prozent des Investitionsbudgets der Gemeinde“ selbst verwalten. Es geht hier nicht um ein Fünf-Seelen-Dorf, sondern immerhin um eine Gemeinde mit mehr als 200.000 Einwohnern. Bregmans Botschaft: Bregmans Botschaft: Demokratie wäre möglich.
https://soundcloud.com/radiomuenchen/great-reset-von-unten/s-8hVwq6ZwygB?
In Deutschland ist das nicht anders. Dabei enthält das als Provisorium gedachte Grundgesetz von 1949 ganz gute Ansätze. Doch bis heute fehlt ihm die demokratische Legitimation, die auch 1990 ausblieb, nach dem Beitritt der aufgelösten DDR. Um aus dem Grundgesetz eine gültige Verfassung zu machen, bedarf es einer Volksabstimmung, die nie erfolgte. Was wir tun können, um endlich eine Verfassung zu erhalten, die den Interessen der Menschen dient, darüber haben wir uns schon im Juli 2021 mit dem Autor und Demokratie-Aktivisten Ralph Boes unterhalten. Jetzt hat er ein Buch geschrieben: „Great Reset von unten – Die ultimative Delegitimierung unseres Staates und die konkreten Schritte, das ganze vom Grunde her in Ordnung zu bringen“.
Unser Autor Jonny Rieder hat es gelesen.
Sprecher: Ulrich Allroggen
Bild: ChatGPT im Auftrag von Radio München
-
 @ 2b24a1fa:17750f64
2025-05-19 11:48:21
@ 2b24a1fa:17750f64
2025-05-19 11:48:21Wo läßt es sich trefflicher plaudern als am Küchentisch. Es muß ja nicht unbedingt der eigene sein. Hauptsache, es sitzen vergnügte Menschen reinen Herzens daran, wie zum Beispiel die Herren Helmut Schleich und Franz Esser.
-
 @ 48706e89:cd3c97e3
2025-05-19 13:06:27
@ 48706e89:cd3c97e3
2025-05-19 13:06:27Mal schauen, was so geht...
-
 @ 48706e89:cd3c97e3
2025-05-19 12:42:25
@ 48706e89:cd3c97e3
2025-05-19 12:42:25# KI und Ethik im RU\ Wlche Verantwortung tragen wir beim Einsatz von KI in der Bildung? Dieses Modul bietet theologische Perspektiven und Diskussionsimpulse."
-
 @ e17e9a18:66d67a6b
2025-05-19 11:46:09
@ e17e9a18:66d67a6b
2025-05-19 11:46:09We wrote this album to explain the inspiration behind Mutiny Brewing, and as a way to share the story of Bitcoin and freedom technologies like nostr. Through these songs, we’ve tried to capture every truth that we believe is essential to understand about money, freedom, trust, and human connection in the internet age. It’s our way of making these ideas real and relatable, and we hope it helps others see the power of taking control of their future through the systems we use.
01. "Tomorrow's Prices on Yesterday's Wage" explores the harsh reality of inflation. As central banks inflate the money supply, prices rise faster than wages, leaving us constantly falling behind. People, expecting prices to keep climbing, borrow more to buy sooner, pushing prices even higher in a vicious cycle. You're always a step behind, forced to pay tomorrow's inflated prices with yesterday's stagnant wages.
https://wavlake.com/track/76a6cd02-e876-4a37-b093-1fe919e9eabe
02. "Everybody Works For The Bank" "Everybody Works For The Bank" exposes the hidden truth behind our fiat money system.
When banks issue loans, they don’t lend existing money — they create new money from debt. You’re on the hook for the principal and the interest. But the interest doesn’t exist yet — it has to come from someone else borrowing. That means the system only works if debt keeps growing.
When it doesn’t, the whole thing wobbles. Governments step in to bail out the banks by printing more money, and that cost doesn’t vanish. It shows up in your taxes, your savings, and your grocery bill.
We’re not just working to pay our own debts, we’re paying for their losses too.
https://wavlake.com/track/4d94cb4b-ff3b-4423-be6a-03e0be8177d6
03. "Let My People Go" references Moses' demand for freedom but directly draws from Proverbs 6:1–5, exposing the danger of debt based money. Every dollar you hold is actually someone else's debt, making you personally liable—held in the hand of your debtor and at risk of their losses, which you ultimately pay for through inflation or higher taxes. As the song says, "The more you try to save it up, the deeper in you get." The wisdom of Proverbs urges immediate action, pleading urgently to escape this trap and free yourself, like a gazelle from a hunter.
https://wavlake.com/track/76214ff1-f8fd-45b0-a677-d9c285b1e7d6
04. "Mutiny Brewing" embodies Friedrich Hayek's insight: "I don't believe we shall ever have good money again before we take it out of the hands of government... we can't take it violently... all we can do is by some sly roundabout way introduce something they can't stop."
Inspired also by the Cypherpunk manifesto's rallying cry, "We will write the code", the song celebrates Bitcoin as exactly that unstoppable solution.
"Not here to break ya, just here to create our own little world where we determine our fate." https://wavlake.com/track/ba767fc8-6afc-4b0d-be64-259b340432f3
05. "Invisible Wealth" is inspired by The Sovereign Individual, a groundbreaking 1990s book that predicted the rise of digital money and explores how the return on violence shaped civilizations. The song references humanity's vulnerability since agriculture began—where stored wealth attracted violence, forcing reliance on larger governments for protection.
Today, digital privacy enabled by cryptography fundamentally changes this dynamic. When wealth is stored privately, secured by cryptographic keys, violence becomes ineffective. As the song emphasizes, "You can't bomb what you can't see." Cryptography dismantles traditional power structures, providing individuals true financial security, privacy, and freedom from exploitation.
“Violence is useless against cryptography” https://wavlake.com/track/648da3cc-d58c-4049-abe0-d22f9e61fef0
06. "Run A Node" is a rallying cry for Bitcoin's decentralisation. At its heart, it's about personal verification and choice: every node is a vote, every check’s a voice. By running the code yourself, you enforce the rules you choose to follow. This is true digital democracy. When everyone participates, there's no room for collusion, and authority comes directly from transparent code rather than blind trust.
"Check the blocks, verify, ain't that hard to do When everyone's got eyes on it, can't slip nothin' throgh." https://wavlake.com/track/ee11362b-2e84-4631-b05e-df6d8e6797f8
07. "Leverage is a Liar" warns against gambling with your wealth, but beneath the surface, it's a sharp critique of fractional reserve banking. Fractional reserves inflate asset prices, creating the illusion of wealth built on leverage. This system isn't sustainable and inevitably leads to collapse. Real wealth requires sound money, money that can't be inflated. Trying to gain more through leverage only feeds the lie.
"Watch it burn higher and higher—leverage is a liar." https://wavlake.com/track/67f9c39c-c5e1-4e15-b171-f1f5442f29a5
08. "Don't Get Rekt" serves as a stark warning about trusting custodians with your Bitcoin. Highlighting infamous collapses like Mt.Gox, Celsius, and FTX. These modern failures echo the 1933 Executive Order 6102, where the US government forcibly seized citizens' gold, banned its use, and then promptly devalued the currency exchanged for it. History shows clearly: trusting others with your wealth means risking losing it all.
"Your keys, your life, don't forget." https://wavlake.com/track/fbd9b46d-56fc-4496-bc4b-71dec2043705
09. "One Language" critiques the thousands of cryptocurrencies claiming to be revolutionary. Like languages, while anyone can invent one, getting people to actually use it is another story. Most of these cryptos are just affinity scams, centralized towers built on shaky foundations. Drawing from The Bitcoin Standard, the song argues money naturally gravitates toward a single unit, a universal language understood by all. When the dust settles, only genuine, decentralized currency remains.
"One voice speaking loud and clear, the rest will disappear." https://wavlake.com/track/22fb4705-9a01-4f65-9b68-7e8a77406a16
10. "Key To Life" is an anthem dedicated to nostr, the permissionless, unstoppable internet identity protocol. Unlike mainstream social media’s walled gardens, nostr places your identity securely in a cryptographic key, allowing you total control. Every message or action you sign proves authenticity, verifiable by anyone. This ensures censorship resistant communication, crucial for decentralised coordination around Bitcoin, keeping it free from centralised control.
"I got the key that sets me free—my truth is mine, authentically." https://wavlake.com/track/0d702284-88d2-4d3a-9059-960cc9286d3f
11. "Web Of Trust" celebrates genuine human connections built through protocols like nostr, free from corporate algorithms and their manipulative agendas. Instead of top down control, it champions grassroots sharing of information among trusted peers, ensuring truth and authenticity rise naturally. It's about reclaiming our digital lives, building real communities where trust isn't manufactured by machines, but created by people.
"My filter, my future, my choice to make, real connections no one can fake." https://wavlake.com/track/b383d4e2-feba-4d63-b9f6-10382683b54b
12. "Proof Of Work" is an anthem for fair value creation. In Bitcoin, new money is earned through real work, computing power and electricity spent to secure the network. No shortcuts, no favourites. It's a system grounded in natural law: you reap what you sow. Unlike fiat money, which rewards those closest to power and the printing press, Proof of Work ensures rewards flow to those who put in the effort. Paper castles built on easy money will crumble, but real work builds lasting worth.
"Real work makes real worth, that's the law of this earth." https://wavlake.com/track/01bb7327-0e77-490b-9985-b5ff4d4fdcfc
13. "Stay Humble" is a reminder that true wealth isn’t measured in coins or possessions. It’s grounded in the truth that a man’s life does not consist in the abundance of his possessions. Real wealth is the freedom to use your life and time for what is good and meaningful. When you let go of the obsession with numbers, you make room for gratitude, purpose, and peace. It's not about counting coins, it's about counting your blessings.
"Real wealth ain't what you own, it's gratitude that sets the tone." https://wavlake.com/track/3fdb2e9b-2f52-4def-a8c5-c6b3ee1cd194
-
 @ 88cc134b:5ae99079
2025-05-19 11:08:56
@ 88cc134b:5ae99079
2025-05-19 11:08:56deded
-
 @ 2b24a1fa:17750f64
2025-05-19 11:45:25
@ 2b24a1fa:17750f64
2025-05-19 11:45:2580 Jahre später und kein bisschen klüger. Dieser Eindruck drängt sich unmittelbar auf, mit Blick auf die heutige, desaströse Weltlage. Dabei hat man sich vor rund acht Dekaden weltweit ein „Nie wieder“ geschworen. „Nie wieder Krieg!“ Es sollte dabei nicht bei einem Lippenbekenntnis bleiben. Der Schwur wurde unter anderem in der Charta der Vereinten Nationen festgehalten. Doch wie kommt es, dass das Versprechen, die Waffen zukünftig schweigen zu lassen, seither unzählige Male gebrochen wurde? War es etwa manchen der Siegermächte nicht ernst damit, als sie sich kurz vor Kriegsende in Jalta zur gleichnamigen Konferenz trafen?
https://soundcloud.com/radiomuenchen/abgrunde-der-gier-von-roger-waters?
Hören Sie hierzu die Rede des Pink Floyd - Mitgründers Roger Waters anlässlich des 80. Jahrestags der Jalta-Konferenz, die auf Deutsch zuerst bei Manova unter dem Titel „Abgründe der Gier“ erschienen war. www.manova.news/artikel/abgrunde-der-gier
Sprecherin: Sabrina Khalil, Redaktion: N. Riedl
Bild: Wikipedia
-
 @ 2b24a1fa:17750f64
2025-05-19 11:40:50
@ 2b24a1fa:17750f64
2025-05-19 11:40:50„Reibung erzeugt Wärme“ – war das Kredo unserer Streitkultur, bis es meist aus dem Ruder lief und einer gekränkt vom Tisch verschwand. Themen nicht anzusprechen war allerdings keine Option. Was bedeutet diese Auseinandersetzung zwischen den Menschen und warum ist sie so wichtig?
https://soundcloud.com/radiomuenchen/die-schnellen-urteile-verzogern-von-markus-langemann?
Vom Streiten, Kommunizieren und dem Schmerz des Menschseins schreibt der Publizist und Herausgeber des Clubs der klaren Worte Markus Langemann.
Sabrina Khalil hat den Text für uns gelesen.
-
 @ 45bda953:bc1e518e
2025-05-19 09:49:40
@ 45bda953:bc1e518e
2025-05-19 09:49:40This post will be edited and refined over time.
Eschatology is the study of Biblical prophecy pertaining to what is commonly referred to as the end times. Bitcoin is the transformation of Austrian school economics theory into an efficient and applicable method driven by natural incentives and free market consensus mechanisms.
What happens when eschatology is viewed through a Bitcoin inspired world view?
In this thesis I contend that it is possible and very probable that the consequences of what Satoshi Nakamoto created in Bitcoin and the prophecies surrounding Jesus Christ with regards to the second coming and a thousand year kingdom of peace and prosperity convalesce into a very compelling argument for Biblical prophecy fulfilment.
...
No one would argue that modern major banks are today more powerful than kings of old and governments are mere puppets to the sway that the banking empires hold over them.
In Biblical prophecy when kings and powers are mentioned people rarely think of banking but nothing is comparable to the immense scale of wealth, power and territory controlled directly or indirectly by banks.
IMF, BIS, the FED and Blackrock are where the levers of power are pulled in the current dispensation. Governments restructure more frequently than these institutions whom endure and exercise unmerited influence over said governments and the public interests they claim to represent.
An excerpt from the King James Bible, Daniel chapter 2 describes prophetically the ages of man and its rotations of power.
Interesting to note that it is symbolically portrayed in monetary/industrial metals. All used as tokens for trade, symbols of wealth and manufacture.
Gold, silver, bronze, iron and clay. Gold has been a dominant symbol of power and wealth through millennia. Silver, brass and iron ores are mainly industrial metals although they all had prominent turns as coinage. Due to the debasement and concentration of gold specifically.
Clay on the other hand is only a symbol of power in construction and iron has never been used in construction to the extent it is in the 20th and 21st century. Skyscrapers are the symbols of money and power today, i.e. big bank and government buildings.
Daniel Chapter 2:24–45
24Therefore Daniel went to Arioch, whom the king had appointed to destroy the wise men of Babylon. He went and said thus to him: “Do not destroy the wise men of Babylon; take me before the king, and I will tell the king the interpretation.”
25Then Arioch quickly brought Daniel before the king, and said thus to him, “I have found a man of the captives of Judah, who will make known to the king the interpretation.”
26The king answered and said to Daniel, whose name was Belteshazzar, “Are you able to make known to me the dream which I have seen, and its interpretation?”
27Daniel answered in the presence of the king, and said, “The secret which the king has demanded, the wise men, the astrologers, the magicians, and the soothsayers cannot declare to the king. 28But there is a God in heaven who reveals secrets, and He has made known to King Nebuchadnezzar what will be in the latter days. Your dream, and the visions of your head upon your bed, were these: 29As for you, O king, thoughts came to your mind while on your bed, about what would come to pass after this; and He who reveals secrets has made known to you what will be. 30But as for me, this secret has not been revealed to me because I have more wisdom than anyone living, but for our sakes who make known the interpretation to the king, and that you may know the thoughts of your heart.
31“You, O king, were watching; and behold, a great image! This great image, whose splendor was excellent, stood before you; and its form was awesome. 32This image’s head was of fine gold, its chest and arms of silver, its belly and thighs of bronze, 33its legs of iron, its feet partly of iron and partly of clay. 34You watched while a stone was cut out without hands, which struck the image on its feet of iron and clay, and broke them in pieces. 35Then the iron, the clay, the bronze, the silver, and the gold were crushed together, and became like chaff from the summer threshing floors; the wind carried them away so that no trace of them was found. And the stone that struck the image became a great mountain and filled the whole earth.
36“This is the dream. Now we will tell the interpretation of it before the king. 37You, O king, are a king of kings. For the God of heaven has given you a kingdom, power, strength, and glory; 38and wherever the children of men dwell, or the beasts of the field and the birds of the heaven, He has given them into your hand, and has made you ruler over them all — you are this head of gold. 39But after you shall arise another kingdom inferior to yours; then another, a third kingdom of bronze, which shall rule over all the earth. 40And the fourth kingdom shall be as strong as iron, inasmuch as iron breaks in pieces and shatters everything; and like iron that crushes, that kingdom will break in pieces and crush all the others. 41Whereas you saw the feet and toes, partly of potter’s clay and partly of iron, the kingdom shall be divided; yet the strength of the iron shall be in it, just as you saw the iron mixed with ceramic clay. 42And as the toes of the feet were partly of iron and partly of clay, so the kingdom shall be partly strong and partly fragile. 43As you saw iron mixed with ceramic clay, they will mingle with the seed of men; but they will not adhere to one another, just as iron does not mix with clay. 44And in the days of these kings the God of heaven will set up a kingdom which shall never be destroyed; and the kingdom shall not be left to other people; it shall break in pieces and consume all these kingdoms, and it shall stand forever. 45Inasmuch as you saw that the stone was cut out of the mountain without hands, and that it broke in pieces the iron, the bronze, the clay, the silver, and the gold — the great God has made known to the king what will come to pass after this. The dream is certain, and its interpretation is sure.”
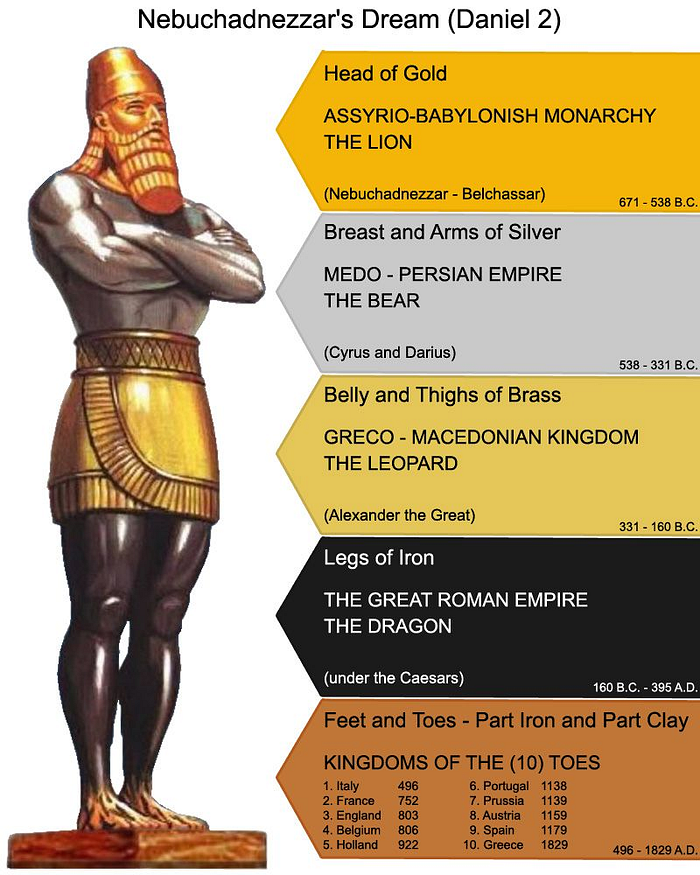 I speculate that the toes of iron and clay represent the world banking empire. Skyscrapers are constructed from iron and cement. Different forms of clay is a necessary cement ingredient. Architecture has always been used as a symbol of dominance by rulers especially true of systems who use awe as a means to cause feelings of insignificance in the individual thereby asserting their power at low cost. Ironically it never costs the ruler to create these structures, the cost is always carried by the people in time, resources and energy.
I speculate that the toes of iron and clay represent the world banking empire. Skyscrapers are constructed from iron and cement. Different forms of clay is a necessary cement ingredient. Architecture has always been used as a symbol of dominance by rulers especially true of systems who use awe as a means to cause feelings of insignificance in the individual thereby asserting their power at low cost. Ironically it never costs the ruler to create these structures, the cost is always carried by the people in time, resources and energy.Skyscrapers and large construction are the modern symbols of money and power. Not so much kings, palaces and temples. The stone breaking the power of the statue has to break something contemporary other than kings and palaces if it is to be eschatological prophecy fulfilled in our time.
https://www.britannica.com/technology/cement-building-material/History-of-cement
The invention of portland cement usually is attributed to Joseph Aspdin of Leeds, Yorkshire, England, who in 1824 took out a patent for a material that was produced from a synthetic mixture of limestone and clay.
https://www.thoughtco.com/how-skyscrapers-became-possible-1991649
Later, taller and taller buildings were made possible through a series of architectural and engineering innovations, including the invention of the first process to mass-produce steel.
Construction of skyscrapers was made possible thanks to Englishman Henry Bessemer, (1856 to 1950) who invented the first process to mass-produce steel inexpensively.
You watched while a stone was cut out without hands,
No hands needed when the stone is an idea.
As a thought experiment, imagine there was a base metal as scarce as gold but with the following properties:\ — boring grey in colour\ — not a good conductor of electricity\ — not particularly strong, but not ductile or easily malleable either\ — not useful for any practical or ornamental purpose\ \ and one special, magical property:\ — can be transported over a communications channel
Greshams Law illustrated in slow motion picture.
1: The banks collapse. Being fundamentally weak because of zero reserve lending, any student of Austrian economics has been correctly predicting banking collapse, and have incorrectly been advocating gold as the solution to this collapse. Many of the big economies are valued through their housing market. Housing will be demonetised (Iron and clay economy) meaning shelter and property will become affordable to the average wage earner again. The large cement and iron structures become redundant. Everyone will work from home and a value to value economy will make banks seem like relics from an age of stupidity and evil.
2: Industrial metal iron will not be for mega structures that contain speculators and bookkeepers who have fiat jobs slaving for fiat money. Iron will be used to improve the lives of individuals. Iron as coinage is already demonetised.
3: Brass is demonetised as coinage and only valuable in industry. Ammunition, music, plumbing etcetera.
4: Silver has been a terrible money throughout history and when the silver investors wake up to the fact that they are holding onto a redundant asset with zero monetary properties compared to the alternative they will dump their holdings, crashing the silver market and subsequently reducing the prices of producing -
solder and brazing alloys, batteries, dentistry, TV screens, smart phones microwave ovens, ad infinitum. To quote Jeff Booth. "Prices always fall to the marginal cost of production."
5: The final Rubicon is gold, people get excited about the Bitcoin exchange traded funds but it is nothing compared to the value proposition when gold pundits, large investment funds, governments pension funds and reserve banks finally realise that gold is worthless as money in this new dispensation.
To illustrate the point more vividly.
Ezekiel 7:19
They shall cast their silver in the streets, and their gold shall be removed: their silver and their gold shall not be able to deliver them in the day of the wrath of the LORD: they shall not satisfy their souls, neither fill their bowels: because it is the stumbling block of their iniquity.
What we are witnessing is the biggest rug pull the world has ever seen. In this future metals will exclusively be used for industrial use cases after being stripped of their monetary premium.
 This collapse is something that happens slowly over a long period of time. More or less one hour.
This collapse is something that happens slowly over a long period of time. More or less one hour.Revelation 18 verse 11–19 (The fall of Babylon)
And the merchants of the earth shall weep and mourn over her; for no man buyeth their merchandise any more: The merchandise of gold, and silver, and precious stones, and of pearls, and fine linen, and purple, and silk, and scarlet, and all thyine wood, and all manner vessels of ivory, and all manner vessels of most precious wood, and of brass, and iron, and marble, And cinnamon, and odours, and ointments, and frankincense, and wine, and oil, and fine flour, and wheat, and beasts, and sheep, and horses, and chariots, and slaves, and souls of men. And the fruits that thy soul lusted after are departed from thee, and all things which were dainty and goodly are departed from thee, and thou shalt find them no more at all. The merchants of these things, which were made rich by her, shall stand afar off for the fear of her torment, weeping and wailing, And saying, Alas, alas, that great city, that was clothed in fine linen, and purple, and scarlet, and decked with gold, and precious stones, and pearls! For in one hour so great riches is come to nought. And every shipmaster, and all the company in ships, and sailors, and as many as trade by sea, stood afar off, And cried when they saw the smoke of her burning, saying, What city is like unto this great city! And they cast dust on their heads, and cried, weeping and wailing, saying, Alas, alas, that great city, wherein were made rich all that had ships in the sea by reason of her costliness! for in one hour is she made desolate.
TLDR - No more money printer go BRRR. means death to the bourgeoisie cantillionaire class.**
Is it realistic to assume that all the worlds monetised industries collapse to fair value in one hour?
Coming back to eschatology, 2 Peter 3:8
But, beloved, be not ignorant of this one thing, that one day is with the Lord as a thousand years, and a thousand years as one day.
Eschatology students use this verse to speculatively project the fulfilment of Biblical prophecies with regards to their predicted time of occurrence. Now let’s apply this to Babylon falling in one hour.
1000 (one day) divided by 24 (hours) equals 41,6 years (one hour)
Since the first block was mined in January 2009 you add 41,6 years you get a completion date of 2050 a.d
Remember, this stone (Bitcoin) becomes a great mountain and fills the whole earth. A kingdom which shall never be destroyed; and the kingdom shall not be left to other people; it shall break in pieces and consume all these kingdoms, and it shall stand forever. The dream is certain, and its interpretation is sure.
But contemporary sources must reflect this probability if it is a good theory.
https://www.newsbtc.com/news/50-of-population-to-use-bitcoin-by-2043-if-crypto-follows-internet-adoption/
If the banking system is first to collapse we can give it +- 10 years and we are already 14 years in since (Genesis Block) the stone struck the feet. People are slow to see the reality of the world they are living in. If all this is accurate then the world banking system is doomed.
https://www.youtube.com/watch?v=exK5yFEuBsk
Regards
Echo Delta
bitbib
-
 @ e97aaffa:2ebd765d
2025-05-19 09:47:30
@ e97aaffa:2ebd765d
2025-05-19 09:47:30Algo que me faz uma certa confusão, é ouvir as pessoas, a afirmarem que será impossível existir um governo e uma economia saudável com o Bitcoin ou qualquer outra moeda não inflacionária. Que o Bitcoin como moeda, iria tornar a sociedade numa anarquia.
A governança da nossa sociedade é baseada em 3 pilares: o governo, económico e moeda. Os 3 evoluíram e se adaptaram mutuamente e em simultâneo ao longo do tempo. Só que essa e evolução, trouxe-nos para um centralismo atroz, onde os governos condicionadam excessivamente a economia e controlam a moeda. Em vez de 3 pilares, temos apenas um, o governo, a economia deixou de ser livre e a moeda é manipulada para financiar o governo.
É claro, se nós mudarmos apenas o sistema monetário, o equilíbrio dos 3 pilares vai quebrar, assim não vai funcionar. O erro é acreditar que é possível mudar apenas um pilar, sem adaptar os outros.
Na prática temos que mudar apenas um (governo), os outros dois é libertá-los. Os governos modernos são baseados em défice orçamental, impostos altos, dívida soberana e inflação monetária para o seu financiamento e para controlar a economia. Como os governos estão altamente endividados e com altas taxas de impostos, só lhe resta a última carta, a moeda/inflação monetária.
Se perdessem o controlo da moeda, seria necessário uma mudança profunda nos estados modernos. Em vez de ter défice-dívida-inflação, teriam mudar para excedente-reservas-deflação, é fazer o oposto do que fazem hoje. É claro que ao podemos apenas mudar de uma moeda inflacionária para uma não inflacionária e manter inalterado os outros dois, isso não vai resultar. Será necessário mudar os 3 para que funcione bem.
É aqui está o problema, será uma mudança profunda nos governos modernos, têm que passar a ter excedente orçamental e criar reservas monetária. Isso vai obrigar os governos a ter muita disciplina e boa gestão, nos momentos de crescimento económico terão que fazer reservas e zerar a dívida soberana. Depois nos períodos de recessão vai utilizar as reservas e se necessário criar dívida soberana para ajudar na recuperação da economia, actualmente os governos utilizam a expansão monetária para esse fim.
Se alguém tem um problema de alcoolismo, não pode apenas trocar whisky por vinho, a mudança terá que ser mais drástica, terá que trocar por água.
Fix the money! Fix the World!
-
 @ 9ca447d2:fbf5a36d
2025-05-19 10:58:20
@ 9ca447d2:fbf5a36d
2025-05-19 10:58:20Panama City may be the next Latin American city to adopt bitcoin, after El Salvador.
Panama City Mayor Mayer Mizrachi has got the bitcoin world excited after hinting that the city might have a bitcoin reserve. The speculation started on May 16 when Mizrachi posted a simple but powerful message on X:
Two words. That’s it. What makes it special is that it came after a high-profile meeting with Max Keiser and Stacy Herbert, two key figures behind El Salvador’s bitcoin strategy.
Keiser is an advisor to El Salvador’s President Nayib Bukele and Herbert leads the country’s Bitcoin Office.
El Salvador became the first country to adopt bitcoin as legal tender back in 2021. Since then, it has been building a national bitcoin reserve, currently holding 6,179 BTC worth around $640 million. It’s also using geothermal energy to power bitcoin mining in an eco-friendly way.
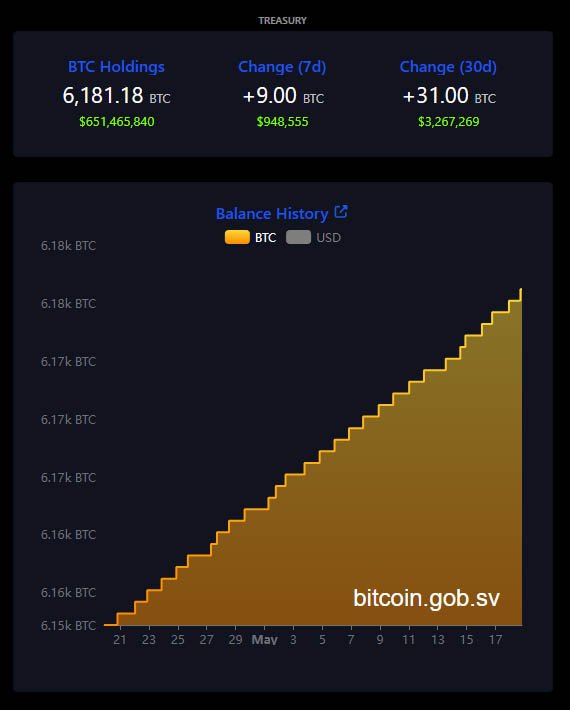
El Salvador’s bitcoin treasury — Bitcoin.gob.sv
Mizrachi’s meeting with Keiser and Herbert was about how Panama could do the same. While the details of the conversation are private, Keiser shared on social media that the two countries will play a big role in the future of Bitcoin.
“Bitcoin is transforming Central America,” Keiser wrote. “El Salvador’s geothermal & Panama’s hydro-electric will power the Bitcoin revolution.”

Max Keiser on X
Panama with its hydroelectric power could be a hub for green bitcoin mining.
Mizrachi has not announced a bitcoin reserve plan nor submitted a proposal to the National Assembly. But his post and public appearances suggest it’s being considered.
He will be speaking at the upcoming Bitcoin 2025 Conference in Las Vegas just days after his social media post. Many expect he will share more about Panama City’s bitcoin plans during his talk.
If Mizrachi pushes for a bitcoin reserve, he will need to work with national lawmakers to pass new legislation. So far, there is no evidence of that.
Even without a bitcoin reserve, Panama City is already going big on digital assets.
In April 2025, the city council approved a measure to allow residents to pay taxes, fees, fines and permits with digital currencies. Supported tokens are bitcoin (BTC), ethereum (ETH), USD Coin (USDC) and Tether (USDT).
To comply with financial laws, the city has partnered with a bank that instantly converts these digital assets into U.S. dollars. According to Mizrachi, this way it’s easier for residents to use digital assets and the city’s financial operations will be transparent and legal.
Another part of the meeting with El Salvador’s advisors was education.
Stacy Herbert confirmed that Panama City will be integrating El Salvador’s financial literacy book, “What is Money?” into their digital library system. The goal is to help students, teachers and the general public understand bitcoin and digital currencies in modern finance.
This is a trend in Latin America where countries are looking for alternatives to traditional banking systems. Inflation, economic instability and the rise of decentralized finance are forcing governments to look into new financial tools.
-
 @ dfa02707:41ca50e3
2025-05-19 10:54:00
@ dfa02707:41ca50e3
2025-05-19 10:54:00-
Version 1.3 of Bitcoin Safe introduces a redesigned interactive chart, quick receive feature, updated icons, a mempool preview window, support for Child Pays For Parent (CPFP) and testnet4, preconfigured testnet demo wallets, as well as various bug fixes and improvements.
-
Upcoming updates for Bitcoin Safe include Compact Block Filters.
"Compact Block Filters increase the network privacy dramatically, since you're not asking an electrum server to give you your transactions. They are a little slower than electrum servers. For a savings wallet like Bitcoin Safe this should be OK," writes the project's developer Andreas Griffin.
- Learn more about the current and upcoming features of Bitcoin Safe wallet here.
What's new in v1.3
- Redesign of Chart, Quick Receive, Icons, and Mempool Preview (by @design-rrr).
- Interactive chart. Clicking on it now jumps to transaction, and selected transactions are now highlighted.
- Speed up transactions with Child Pays For Parent (CPFP).
- BDK 1.2 (upgraded from 0.32).
- Testnet4 support.
- Preconfigured Testnet demo wallets.
- Cluster unconfirmed transactions so that parents/children are next to each other.
- Customizable columns for all tables (optional view: Txid, Address index, and more)
- Bug fixes and other improvements.

Announcement / Archive
Blog Post / Archive
GitHub Repo
Website -
-
 @ 45bda953:bc1e518e
2025-05-19 09:17:30
@ 45bda953:bc1e518e
2025-05-19 09:17:30Emilien stepped into the space motel's bar. The area was dimly lit and the music was unbearably loud. At least all the tables and sunken lounges each had their own lights and sound dampers. He stepped up to a table and pushed down on the receptor to reduce volume. He could not think with the noise. He looked around for Macy and inconspicuously acquainted himself with the current patrons in the establishment. He pulled his hoody further forward when he noticed the android in a wheel chair. "Not my type of company." He thought to himself. In the centre of the room a couple was having a spectacular time, an empty bottle on the table, they were specimens of myth. The guys muscles were chiselled, with tight fabric clinging to his body specifically to display every contour of his physique. His female counterpart wore loose material with translucent green tattoo's running up her body like pin stripes shining through the thin cloth hinting at a perfectly balanced pose and feminine silhouette underneath. Emilien swiped on the tables interface to call for the proprietor. He folded his arms and leaned onto the table tilting his head down slightly to keep shadow on his face. Macy entered the room through the kitchen swivel door. She was holding an empty tray and a serviette draped over her arm. She walked straight over to Emilien's table. "Good rotation sir. Welcome to Macy's. Are you a regular customer or is it your first visit to my fine establishment?" She seemed concerned and worried. The corners of Emiliens lips curved up a little. Keeping his head down teasingly. "Sir? Do we have an existing open channel?" He ignored her. "Sir, If you don't have liquidity I have no services to offer that you cannot get off your own ship." Emilien looked up with a gleam in his eye. Macie's posture relaxed with a sigh of relief. "Emile, you fuck. You freaked me out." "I'm sorry, I could not help myself." He waved a halfhearted greeting, slightly laughing. "You know I have some new rules around for you nano augmented types." His aversion to the word rules was evident only to himself. "Like what?" Macy felt apologetically obliged to explain the nature of her circumstances. "I had diplomats from the outer void regions come for a private meeting. Financial in nature. A spacer customer arrived blocks before them, I did not suspect him of anything criminal." She put the tray down and gripped the table with both hands shifting her weight. "His routine for meals were already established, he managed to spy on them through my privacy protocols and hacked their clients. He participated as a ghost during most of their stay and dealings." Emilien whistled. "That's rough, how did you handle it." "I did not do anything." Her dreads shook as she moved her head in animated frustration. "No one knew until they all had been gone for blocks. My reputation took a serious knock. They made a claim against me, I was accused of being complicit. Emilien glanced back over his shoulder when he noticed the android cart himself around his table. "Warren helped me and found all the dirty code and sequestered it. We have all the data and footage, it proves beyond a doubt that I was not involved. Thank god for the core otherwise my whole station might have been destroyed by now." Emile gave a sly look. "How do you know it was not me who stole the data?" She locked eyes with him. "You still have the same face as before bro and I know you won't fuck with me. I'll force close our channel." She joked with serious tone nudging him with her fist playfully. She was generally perceived as strict and militant because of her Shiv citizenship. Shiv military training and service was compulsory, all respected the Shiv in their traditions, their ways were isolationist and exclusionary in nature. Emilien has seen her use military style jujitsu-boxing to neutralise and boot out unruly customers. The Juel woman noticed the out of character friendly gesture Macy made. The unexpected interaction drew her attention from across the room. "So, what is this rule of yours." Macy seemed reluctant to say. "I'm sorry bud. You'll have to swallow a slipper pill every 576 blocks while you are on this station." His shoulders sagged and could not help but bounce his leg on the rail under the table. "Really?!" "Yes, really. I have to retain my customers trust and neutralising all augmented customers body gadgets was the unanimous way to go." Emilien seemed pissed. "Your customers might not know that I'm augmented. And what if I don't plan on staying that long. I just want to see Warren then I'll be off." Macy shook her head. "Warren is passed out in his ship and will probably wake up with a very bad hangover. He partied with the Jeul pair and their entourage for most of this rotation, you know how he gets." Macy waved her hand towards the couple who seemed to be looking directly at Emilien. He looked straight back at them and swiped the interface's privacy command dropping a vision distortion field around his table. Encapsulating himself and Macy. "I treat everyone the same, no compromise." Emile looked at her in a moment of rumination. "Let's get it over with." Macy removed a container from her moonbag after opening, holding it towards Emilien he took the purple capsule and swallowed it without a drink and opened his mouth wide moving his tongue around to show Macy that he did indeed swallow the prophylactic. "And what about robo-mech boy back there? He cannot eat slipper pills." Emilien sounded annoyed and regretful." Macy gave him a stern look tilting her head in annoyance. "Why do think he's in a wheelchair, you know I can't talk about my customers with my customers? Besides from the obvious." Emilien did not say anything. Macy sighed. "What can I get you sir?" "I'll just have a beer." Macy stepped out through the distortion field and became a messy disfigured indistinguishable form. Emilien pushed the music's volume up and waited for the inevitable. He sensed the actuators in his shoulders, elbows and wrists disable in sequence down his arms. His spines bit rate slowed to a crawl and the lack of connectivity to his neck port was becoming noticeable. His legs went numb instantly. "Now I am nothing more than a pathetic land crawler." He felt weak and vulnerable in his natural form. His mental state bordered on the fringes of stable and paranoid, fearful thoughts threatening to manifest in his mind. He saw a figure approach. He assumed it was his drink. The slender glowing tattooed leg of the Jeul woman pierced the veil. A bright green line that suddenly dims where her skirt begins. She stepped through the curtain with a friendly nonchalant expression. "Mind if make your acquaintance mon ami?" Emilien dropped the barrier and lowered the volume making sure that he was back on visual record of Macy's archive. "Not really, thanks, I'm good." Macy returned to place a cold beer on the table. The interface flashed a price in femto-sat and Emilien tapped his ring on it shifting 11 fSAT from a mini holographic Bob to very happy little Alice. The animation morphed into a small firework display and died. "Back to work now." Emilien grinned at Macy thankfully and took a sip. "Me and my brother we are celebrating our seventh birth block anniversary." He looked around sarcastically. "You chose a display of death above the resorts on Juel to celebrate your seventh birth block?" She stiffened her glittery lips and raised her eyebrows thoughtfully and took a seat without invitation. "It is more of a tour than a celebration, I am Maurelle Giovanni and my brother is called Lionel also Giovanni obviously. He is my twin baby brother." Emilien looked over at the guy who seemed to be occupied playing a mini game on their tables interface. She tilted her head into his line of sight forcing him to look at her. "Who are you?" "None of your concern really." She did not accept the short stated answer. "No one comes alone all the way to a dead end system just to drink a cheap beer. I am guessing you are a treasure hunter, no. Looking for artefacts of the ancient world, yes?" Emilien had assessed her body language and concluded that her whimsical imagination was one he could easily manipulate. He had enough information to realise that he was faced with a spoiled individual whose sole interest in him was simple curiosity, motivated by boredom and she had a fascination of the mysterious. She seemed like prey but his hunting instincts felt dead inside his disarmed body. His respect for and dependence on Macy also inhibited his urge to exploit it. He shifted his attitude and personality slightly, just enough to not be overbearing. "You make very good estimations, you are wrong but not far off. My name is Scott. And yes I am fascinated, not by the planet and it's relics but by the the secrets of these gates." Her eyes gleamed with amusement and intrigue. "You like secrets, huh? You must meet Warren. He knows more than the esteemed professors about the gates and their technology." Emilien nodded in agreement. "You said you are Giovanni. Like the Giovanni?" She seemed excited at the prospect of making a new friend and swiped the interface. "Hold this thought, I am going to get myself another drink you are good? No. Food maybe?" "I am good, no wait, another beer." He tipped the bottle toward her in salutation. She stood up taking his bottle with her to the bar. He looked back and was immediately aware that he did not notice that the android wheel himself out and into the conduit. He would have liked to see which of the two entrances of the tube he used to go to his ship. His feeling sorry for and pitying himself put him in a position where he let slip an opportunity to understand and predict the circumstances of his current tactical situation. Never at ease, always being prepared. He felt spite. The girl returned with a beer and a half full whiskey glass, no ice. She reclaimed her seat looking at him. "I am a direct descendant of the patriarch Maurice Giovanni, one of the four primary key holders of our people. There is nothing special about me really, ten..." Emilien cut her off in gentle tone. "Ten percent of the Juel population are descendants of the four patriarchs." Emilien finished her sentence for her. "You are an interesting man Monsieur Scott. What else do you know about me?" Emilien leaned towards her. Noticing her brother yawning across the room. "I know that you are bourgeois and I know that you receive a cyclical allowance from your great, great... How many generations?" "I am removed 133 generations from my Patriarch. He is a very good, doting grandfather. We all adore him. We are around 750 million siblings you know. Those who are from aristocracy have fewer children than the proles. We are so few so that our wealth is not diluted too much." She smiled reminiscently dragging her finger on the edge of the glass. Her brother seemed to stretch himself out he stood up and walked over. Entering the sound damper he acknowledged Emilien's presence with a curt nod. "Maurelle, I am going to sleep." He said to her. She waved at him dismissively. "Have a good dream frere." He exited the room through the right tubes door which made sense as their ship was more closely attached to it on that side of the circular docking ring. Predictable and honest Emilien thought to himself. Macy popped her head through the kitchens serving window. "Lights out and shutdown in 2 blocks. Just a friendly notice." The couple acknowledged the warning from Macy with raised glass and bottle. Emilien turned his attention back to the lady. "How do you manage to retain wealth in such a large family?" He pretended to be ignorant of the finery and detail of Juel culture. "We have closed loop channels controlled and balanced by the patriarchs. But our money is good as core stone. Anywhere in the outer void. Only recently has dispute arose between my Patriarchs and the Magarrie. They do not accept our Sats anymore since the war started. They only accept bitcoins directly from the core. I was only four cycles old when the war began so I am used to it." Emilien felt a conflicting disturbance, thinking about how his body is only two cycles active but his mind stretches back far beyond this time. Being both older and younger than his partner in discourse. "Helloo? I lost you there for a moment Scott." "What are you thinking about?" Emilien lied to her faking emotion. "I was just thinking about the tremendous loss of life that we are orbiting. The planet embedded with what it's inhabitants assumed would be it's portal to prosperity became the golem of it's demise." He was happy that Maurelle seemed to empathise and mirror his philosophic grief. "Come with me I want to tell you a secret. You like secrets." She stood up taking his hand gently tugging, compelling him to follow her. She led him to the far end of the room. She pulled a small levered switch and the wall folded in on itself to reveal a impressive window flooding sharp light into the whole of the large room as it retracted. They both squinted and lifted their hands to shield their eyes adjusting to the glare of Sol. The scene of destruction appeared even more dramatic and morbid as dark sharply defined shadows clipped with golden edges, evoking a sense of isolation and suffering. "These gates were supposed to be a gift to Earth. A hope of spreading humanity across the stars like the children of Abraham." Emilien smirked. "You believe that nonsense?" She rested her head on his shoulder still holding onto his arm. "Our patriarchs have preserved the mysteries of mankind for millennia. I said that I am going to tell you a secret don't patronise me. I do not believe anything. What I know, it is not faith. It is understanding. Knowledge, a type of knowledge that you cannot quantify with mathematics and chemistry. It is a higher science that is proven by the unmistakable coincidence of fate. It is invisible to those who are ignorant and they who despair, those who have lost all hope are blind to this promise." Emilien felt a strange remorse. "I guess I must be blind then." The lights suddenly shut down and the song stopped dead in it's track, like Macy promised. Overcome by the majesty of the scene Maurelle wiped a tear away fearing that her makeup might get ruined. "Anyone can see. They must just open their eyes voluntarily and be honest with themselves. Their true original selves. Who they were made to be." Emile felt judged and wanted to end this conversation quickly. "I am going back to my ship, you have a good night now." She grabbed tightly at his wrist almost painfully. "You do not want to know my secret?" Emelien was becoming annoyed with her insistence he removed her hand from his arm. "I don't think you know any real useful secrets, sweetheart." He sounded threatening, the real enshrouded unmistakable him breaking through the act. She looked at him unintimidated by his sudden shift in personality. "Oh, so I suppose you know why the Juela are at war for most of our lives?" He sarcastically extended his arms forward palms up in restrained but evidently mocking adoration. "Please enlighten me priestess." "They are fighting over this." She pointed at the epic scene of destruction drifting statically out of view as the stations rotation cut it off at the edge of the window. The shadows chased Sol light away sliding like a retracting blade across the room leaving it dark. Emilien burst out angrily. "They are fighting over satoshis! That is all they ever fight over! What I fight for, Damnit! Sats and the resources to gain more of it! That is the beginning and end of all things! Anyone in the universe with even the slightest lick of self worth works, fights and dies for sat!" Maurelle stared astutely at him unemotionally affected by his outburst. She obviously had experienced this exact reaction before and suddenly Emilien realised that he might be the one being manipulated by a smarter and wiser being than himself. "Are you done my love? Have you made your point or is there some other deeper understanding you wish me to internalise into my ignorant small little world?" She threw at him a spiteful sarcasm of her own. "Do you really think I do not know what it means to be seduced by wealth? Luxury?" She took a step closer to him. "Pleasure?" Emilien felt stupid and disarmed this time adding emotionally disarmed to the defeat of being inept in his own body. "I am not a fool mon cherie. The truly wealthy don't fight for wealth, they fight for power. But the noble and sincere fight a different fight with a different weapon. They use words to fight, ideas to win. They fight to gain trust with words, and they fight to retain it with consistency in their actions. Trust is a currency that makes sat seem like shit in comparison because it is real even though you do not believe what you cannot hold in your hand, like your beloved sat." She pointed at the ring on his finger. "Trust only retains value if you honour your words with your actions. Its value is fragile and can disappear in a moment of weakness like water vapour, cherished as the source of life then gone, poof, evaporated. Like magic. This type of trust if gained and retained correctly, projects you forward into the realm of immortality." Emile felt stung and hurt on a personal level, unsure if she was generalising or targeting his own specific weakness purposely. It confused him and made him feel insecure. "What are they fighting for then?" He asked slightly surrendering to the unexpected superior reasoning. Maurelle appreciated the honesty she identified as sincere. She gently took his hand again and led him back to the large convex window. They stood silently for a block, waiting on the rotation to pull the bright light of Sol back into the room. "They are fighting for the power to do that." She pointed at Earth in all it's terrible glory. "The destruction caused by the gate was a terrible cataclysm outside of humanities collective control. The core and the gates are a mystery to mankind." She looked up at Emilien, relieved to see that he was still taking her seriously. "The Maggarie have discovered a weapon that has the power to destroy a planet. The Juel think they are fighting to free Osteri captives from slavery but the real motif is hidden, our Patriarchs unadmitted fear of being inferior to the Maggarie. Most of the goods we traded with them they have stopped accepting, the Shiv and Osteri still buy our products but the Maggarie have suddenly lost the need for our produce, even raw material in it's basest forms. They are expanding somehow and the balance of interdependence has tilted out of our favor. They have no more need for us and have cast us aside like a filthy rag." She paused in thought. "Their new super weapon is the cause of this conflict monsieur Scott." Emilien shrugged. Feeling relieved at regaining the intellectual high ground he thought he had lost. "I'm sorry Maurelle. I have no data on this weapon. If this was true the forums on my bulletin board would have leaked information about it's existence epochs ago, it's been just over three cycles everyone would have known this by now. It sounds more like Jeul fearmongering or perhaps it is the daydreaming fairy tale of an innocent naive girl who worships old myths and legends of a time dead for thousands of years." He pointed at Earth. She sniffed away a hint of emotion and anger. "Well then, I have nothing more to say to you, Good night monsieur Scott." She pulled away from him pridefully and looked out at the enormous gate embedded like a knife into the earths crust. "You are a swine monsieur Scott, leave me alone with my pearl." Emilien stepped back mockingly bowing slightly. "Good night sweetheart." He walked back to his craft laughing inside himself. "Stupid woman." He muttered, although be it doubtfully.
...
scifi
-
 @ 45bda953:bc1e518e
2025-05-19 09:16:17
@ 45bda953:bc1e518e
2025-05-19 09:16:17Core Divide - Sol System - Gate 7
Tremors from warp turbulence rumbled a bit excessively to the Stripper's liking. Emilien was occupied in the lavatory, inspecting and pulling at his face, staring intently at it in the vanity mirror. Macy's establishment was a popular place and he had concerns about who he might run into, contemplating whether he should stick some silicone cosmetic pads onto his face, just enough to obfuscate his current identity. Maybe he shouldn't bother because he might die soon anyway. He has grown fond of his current persona and wouldn't mind retaining it a cycle longer at least. Being artificially immortal somehow did not take away the terror of confronting death. He recalled the various deaths he had experienced and could not decide what method of passing through he preferred, imagining the many shells of himself in different states of necrosis all over the greater void. He considered the possibility that he might not even be himself anymore. He felt like he knows himself well enough to be sure but that small fragment of doubt always gnawed at the back of his mind. He stood back from the mirror. "Am I him?" The ship shook again breaking his stare, he looked at the dental lever lying in the basin and committed to the more necessary procedure, placing the edges of his palms on his chin pushing abruptly up and back dislocated his lower jaw leaving it to hang loose on his face. Taking the root lever from the basin and leaning into the mirror he expertly wedged the tool in behind his rearmost left molar and twisted it slightly, dislodging it. Catching the small object with his left hand he pressed it into a recess on a black ring which he tightly twisted onto his right hands index finger. He narrowed his eyes at the skeletal horror on the other side of the frame inspecting the freshly opened hole. He opened the vanity and took a cartridge which was labelled "AdrenoChem" he removed the object within the container and wiggled it into the vacant molar cavity. Drool dripping into the sink in spite of his reflexive swallowing, he gripped his jaw tight and in gentle circular downward motions found the spot and clicked the joints back into relocation. Chattering his teeth together while stretching his neck he decided to procrastinate on the disguise idea. Emilien went back to the cockpit. Sitting down at the helm he pulled up notices and reports on the divide's situation with regards to the cease fire between the two warring factions. "Tch, tch, tch. This blockade is not making things easy." His eyes were scrolling over bullet points of news headlines when his ship dropped out of warp at the designated coordinates. He switched the display on the primary screen to clearview. The scene of a dead planet, cracked open like an enormous fruit with scattered asteroid clusters and rocky debris appeared onscreen. A giant still wreck of a superstructure resembling parts of an anchor and drift gate joined to each other like Siamese twins, sharp flashes emitting from it silently, like a muted storm in the far distance. He slowly tilted his head to it's limit. Nothing looked familiar to him. He took the console, rolled and yawed simultaneously until his point of view made sense. "There we are. You're not there till you know it." Macy's space motel pitched into view like a tiny reflective insect. On a secondary screen he zoomed the display to fit. It was attached to a large tubular docking link reaching away distantly and back to itself like Ourobouros. There were four spacecraft docked around it's circumference, less than he had expected. He only recognised the largest ship, Warren's vessel. It looked like a mess of odd protrusions, parabolic dishes and bent antennae. Very unsightly, especially compared to the Lux Void Yacht docked across from it. Tourists from everywhere frequented this remote region of the great divide for obvious reasons. Primary motivations were curiosity, pilgrimage, seclusion and scientific research in that order. Macy was smart to settle her establishment at this specific site. Emilien checked web connectivity to make sure he was still well outside the data scrambling anomaly. According to legend, after the Viper gate had been released from the Core and travelled the required distance to it's anchor coordinates, it was supposed to propel it's drift gate into the greater void, but something went wrong. It malfunctioned on it's attempt to release and veered off course being pulled into the orbit of the Sol system. No one knows exactly how it happened but it was clear to see that the energy released was spectacular. The root planet and most of humanity perished in a second, those who survived on the dark side of the collision died from starvation and gradual planetary destabilisation. Emilien morbidly recognised the historicity of the treacherous looking voidscape. Pulsing his ship softly forward caused a cut to core connectivity activating a repetitive red warning light which he promptly covered with one of the intact disposable cups that were rolling around his feet. There is no way to turn the annoying emitter off and he usually ignored it with closed eyes or looking away when void jumping. He is never vulnerable to core connection loss unless he comes to this region or when he is purposely trying to disappear. Researchers have concluded that the interference was broadcast from the gates enormous husk's residual power and intermittent energy discharge. He reverse pulsed back out of the disturbance, the dimmed light under the paper cup died. "Astrid?" "Yes?" He carefully uncoiled the cable and leaned forward connecting himself to the command interface and resting his head on his arms. "Save me." A quick upload took place. "You are welcome commander." Emilien did not respond. Just grateful that if something went askew he would at least wake up knowing that the last thing he saw was the monumental vestige of humanities ancient resting place. And all the ship types docked at Macy's. He smiled at the floor.
...
scifi
-
 @ 45bda953:bc1e518e
2025-05-19 09:15:47
@ 45bda953:bc1e518e
2025-05-19 09:15:47Hithe III
The counsel convened and an area of land had been designated as suitable for an industrial scale landing site of tier III size void vessels. All Kaspian land owners were required to donate workers for the initiative. It was an exciting affair for all involved. With an evergreen tree line to hinder the on and off breeze, tables were assembled and covered with a unique assortment of table cloths. Every lady brought one along and the embroidery on each was the cause of many flattering remarks. The women brought all sorts of food and refreshments, had gazebo's set up and had chairs placed well away from the noise and dust of the demarcated construction site. The men where organising equipment, measuring bedrock depth and organising the labour parties into manageable groups. In spite of all the mothers most dire warnings to stay clear of the areas where active construction would be taking place, the children knew they had free reign to explore and play wherever they wanted. The oxen bellowed incessantly, tethered in long lines before their carts, a slave armed with standard bullwhip, ready to man his post atop each wagon. Albin sat on the ground chewing on a stalk of wheat. Being barely old enough to help the men with their work, he was ordered to do nothing more than spectate. Having received concerned looks from the adults, repeating tropes of how he might get hurt and be in the way. He made peace with his lot. The fact that he was going to see void craft was exciting enough to satiate his curiosity for adventure. He would inadvertently lean back and look up expectantly only to see the clear sky then rock forwards back to his previous position. His only regret was that Seth was not with him to discuss and share in the experience. Seth was old enough to work alongside the other slaves, robbing Albin of good company. He glanced back at the large groups of women and smaller children, his mother stuck out like a sore thumb seeing as she was the only lady wearing pants amongst the variety of her chemise, spring attired peers. Her hair was braided and she had an unopened parasol at hand. No one dared ask why her odd choice in outfit though you knew they thought ill of it by their confused and somewhat unduly patronising looks. Before dawn, when they were still at the manor Albin asked her why she was dressed funny and she said that she would prefer not making a spectacle of herself. He just shrugged and did not think much of it again until just now. It seemed to him that she was the only spectacle around not even having brought a table cloth to adorn her bench like the other woman did. He decided to get something to eat and drink because the texture and taste of the dried stalk had become slightly off-putting making him spit out little bits of grass as he stood up. Cleolia smiled affectionately when she saw her boy approaching and peered over her shaded glasses. He lifted the picnic basket off the ground and put it on the heavy bare wooden table, filled a cup with milk and swallowed it down almost as quickly as he had poured it. "Are they going to be late." He asked his mother. "I'm sure they will arrive soon my dear." She replied while taking a seat in a folding chair. Albin grabbed a handful of pretzels and looked around ponderously as he ingested the snack. The people always enjoyed community gatherings of this sort. Lot's of catching up and gossip happening in a cheerful non insidious way. A type of orderly chaos that brought feelings of peace and tranquillity to the conscious observer. His daydream was broken by a soft but clearly distinct repetitive dong of the distant church tower. His dad and father Ecknard were there using the comms, he assumed they were signalling for something. A long shrill whistling sound caught Albins attention and he began walking towards the furthest groups of men while scanning the area intently. The discernible pitch of Seth's whistle became audible again and Albin honed in on the direction the sound was coming from. He saw his friend standing on an ox cart waving his woven satgat frantically trying to get Albin's attention. As soon as they established eye contact he pointed in a very specific north western direction upwards at the dome of the sky. Albin followed his gaze and for a moment thought his mind is playing a trick on him, but it became apparent that a silhouette of something oddly pale was stuck in the sky with nondescript features. Recalling his studies he managed to identify the craft. It was a Dragon IV Cargo vessel. A Magar craft and supposedly very impressive, the distance did not do it justice, yet the uncanny feeling that X fold more people were floating in a box in the sky than were on the planet made Albin's stomach flip and he felt off balance. He sat down on the ground again to prevent him from stumbling around trying to keep his legs under his body. As soon as the church bell ceased it's tolling a smoke signal was ignited in the clearing beyond the work parties. The yellow smoke billowed up in sharp contrast to the greenery of the fields. III percussive shots thundered through the air like cannon fire causing a sudden change in environmental ambience. Birds were visibly swarming up from trees as far as the eye could see. Albin chose not to remove his sights from the giant void craft. He saw a light in the atmosphere that became distinct as it neared separating into the underbellies of III descending craft. Albin murmered. "The Dragons payload." His excitement grew as did the vessels on their approach. At first a hum growing into a crescendo of weird harmonic roaring as the vessels fought mightily to resist Hithe's above average gravitational pull. All the men tipped their satgats and hard hats to cover their faces, the oxen also faced away. Albin did not want to look away but was forced to turn his head as a powerful gust loaded with projectiles of sand and grass peppered his face sharply. Looking back he saw his mother promptly opening her parasol and pointing it in the direction of the landing, then the real spectacle occurred. All the woman covered their faces only to have their skirts blown up exposing their undergarments, in turn trying to push down their skirts uncovering their faces. The risk of shame weighed against tolerance to pain combined into a beautiful ballet of embroidered cloth being wrapped around trees and condiments strewn around the shaded grove with gazebos escaping the scene followed by children running after them in heated pursuit. Cleolia's pant legs fluttered rapidly around her ankles. As soon as the III vessels turbulence settled she folded her parasol and reassumed her previous position as if nothing of note had transpired. Smiling carefree amongst the distraught group women and children around her. Albin would have laughed at the scene had his eyes not stung so badly. "Mother always knows best." He mumbled to himself as he stood up brushing dust off his undercoat. The opening of the ships cargo bays where announced with a loud hiss of air depressurising. Albin casually sauntered over to get a closer look. The cattle marched up the ramps wagon in tow to park directly alongside the freight. The goods consisted of thousands of long coach bolt like nails as long as fence posts and sturdy modular steel plates stacked on mobile pallets and tied down securely. Albin imagined them to look like giant, shiny metal puzzle pieces. The primitive vehicles and their crews made quick and efficient work of releasing the straps and with the help of overhead cranes hoisted the pallets and their contents into the wagons. Two uniformed men came out from inside the ship and stood watching the men unload their craft. Albin noticed the smartly dressed pilots. "Holy servants of the Empire." He spoke softly under his breath. His desire to meet these champions of the void felt necessary to him. They who travel among the stars much like the stories he always heard about his parents. The men were standing safely apart from the work parties, Albin mustered the courage to approach them. He timidly walked up behind them. "Ahem, Hallo Sir." The pilots looked around surprised. Albin seemed respectful and quaint. "Hey kiddo, you guys have a lovely planet." The pilot replied friendly. "What type of craft are these, sir?" The man gestured towards his vessel in reply. "These? They are standard Type I Droppers. Nothing really special about them." Albin nodded. "Are you from Magar void?" "I am indeed. It is really magnificent but you have something quite spectacular yourselves." Albin did not expect that anything in his little world could impress these well travelled gentlemen. "Like what?" He insisted questioningly. "Like the sol shield. You know the star inhibitor. It's a marvel of our time." The man pointed at Ceb. Albin understood. "Oh yes, my pa put it there so we can all survive here." Both pilots looked at each other surprised. Their demeanour changed and Albin suddenly felt uncomfortable. The man knelt down until he was eye level putting his hand on Albins shoulder clenching it just tight enough to not be painful. "If you are a Domitian heir, then I am an Osteri dancing girl at a Juel gentlemans club." His sarcastic tone cut Albin's pride. "You'd better run along and go play with your friends before I decide to arrest you or report you to the authorities." The other pilot looked away ignoring Albin's confused expression. The man assertively shoved Albin away from him. Albin just barely prevented himself from falling on his rear. Tears welled up in Albin's eyes, he turned and ran away humiliated and angry. But he choked back the tears, choosing to embrace the anger in place of emotional release. He ran away from the construction zone also avoiding the picnic area. He did not want to be around anyone. His erratic and emotional mood would betray his experience if anyone he loved interacted with him. He ran into a shaded area of wood and sat down on a stump to digest and try to reset his state of mind to normalcy. He sat quietly for about III blocks when he heard laughter from beyond the wood. There were a group of boys standing circled around an Osteri boy and girl. The girl was crying. Albin witnessed the interaction. "You are not supposed to be here. Only the working slaves are here today." The boy pleaded with his captor in reply. "I only came to find my sister, we are going back to the village now. Please let us go." "But what was she doing here then? Huh?" Albin walked into the centre of the fray interrupting the entire affair. Standing squarely in front of whom he assumed was the primary instigator. The biggest guy in the bunch. "They are only curious to see the void craft. That is why we all came here today." He explained diplomatically. The big kid sneered. "And who are you to tell me how to treat slaves. You are Magar, you should know better." Another kid piped in. "My mama told me he is Kaspa." The bully looked around surprised. Another boy opined. "Not true, my mom said that his mother was pregnant for 40,000 blocks." And then another kid had to add his understanding to the discussion. "No, no, my pa said that she lost the baby at birth and adopted a slaves child." Albin got overwhelmed with the revelations of rumour and petty gossip surrounding his person. "That does not give you the right to bully them!" Albin pointed to the brother and sister. The big boy smiled a snide retort leaning forward mockingly. "No, but I might have the right to bully you, Osteri bastard child of a slave." Albin felt all natural sense of humanity drain from his being. He turned feigning to leave, balled his fist and swung, socket-ting the unprepared target square on the throat. He fell on his back and the angst of restricted breath became evident first to himself and then to all watching. Albin turned to the siblings. "You can go." The pair hurriedly left and none of the boys even hinted at preventing them. Albin looked at all the others dead in the eye each in turn. Then he left walking the long distance towards his mother. He was thirsty and his hand smarted a little, but he felt much better.
...
scifi
-
 @ 45bda953:bc1e518e
2025-05-19 09:15:17
@ 45bda953:bc1e518e
2025-05-19 09:15:17Emilien was hanging face down inside an enclosure of thick egg shaped glass attached to a mechanised vehicle. Kevlar webbing hugged him tightly into a bucket seat. Long hydraulic arms being manipulated intuitively by a console in his hands and a module interface plugged into his cybernetic neck socket. The bulky animated machine clung like some Lovecraftian spider to the outer hull of his space station. Some cycle’s previously he did data security updates and backtesting for a deep space mining company's security protocols. After seeing their utility, enquired if he could purchase one as partial payment for his contract. Unfortunately they had none for sale but were willing to give him a retired malfunctioning unit gratis. He purchased a maintenance manual on the void web and had connections who helped him source some replacements for the faulty parts. Since then the machine enabled him to be functionally productive in the void, giving him the degrees of freedom and fine motor skills necessary to perform upkeep on stationary deep void assets. The glass of the egg auto dimmed as he laser welded tightly slotted panels together on the previously damaged space station. “How do you feel?” He asked. Abruptly breaking hours of silence. “I’ve been playing around. My capacitance recharge responds well to dump loads, turret retraction gears all functional again. I feel good.” Astrid responded. “Nice. Slowly pressurise the holding chamber for me.” “In progress.” The spider crawled several meters out of the way to safety. Emilien's eyes scanning up and down for leaks. “Slowly babe.” Some minutes passed. “Fully pressurized and stable.” The mechs giant front arms extending, lifted as it stood up on its four hind legs throwing an arachnid shadow across the hull. Emilien flung his arms down crashing a violent concussive blow to the hull in a thunderous clang. The arms retracted. “Still good?” His demeanour remained unchanged. There was a pause. “All good.” Astrid replied. Emilien smiled, Astrid was the best and his feelings of endearment were genuine. “Can we power up the chamber through a fused circuit.” He sensed a soft hum throughout emanating from deep below. “Is the body stable?” “The body is stable. Cryogenic chamber battery backup is at forty three percent. Charge reapplied. Potential of clone spoilage averted. Well done commander.” He could up the ante of risks knowing that his reserve life was secured. “What’s next on the agenda?” “Firstly, signal quality from the drift gate is poor and I am losing connection to the web intermittently.” Emilien nodded. “The gate’s been moving further away. It’s a line of sight problem. I’ll place a relay outside the asteroid belt.” “Secondly, we should see if the husk on the explorer vessel has intact data or a black box. Someone might be looking for them.” He heaved back and vaulted himself off the station in the direction of the wreck micro thrusting for minor trajectory adjustments, with an elegant crash he finally perched on the ship, it gained an almost imperceptible drift as it absorbed the weight of Emilien’s mass, pushing debris along with it. His size would not allow him to move through the standard doors and passages so he opted to disassemble, cut and break apart the hull adjoining the bridge. When he had broken open a space of sufficient size to manoeuvre through, he powered the backlights on, he first peeked inside to familiarise himself with the layout. The egg suspended itself in front of the opening. It was a standard enough bridge doubling as an unorthodox crypt. There were three sets of boots, overalls and coagulated blood all jammed into the slit of the semi sealed door leaving the bridge. An assortment of rubbish floating around casting doubled up shadows larger than themselves. Emilien looked at the mess with sullen eyes. “Shit heads.” He mumbled to himself. All the seats had their safety belts buckled correctly . He concluded that what they experienced must have sucked pretty bad. His mechanical exoskeleton slithered and gripped like an octopus as he entered and positioned himself before the primary interface. His vehicle plugged itself into the command terminal, measuring resistance for shorts before powering it up from his suit. “Can you pull the data and dump it somewhere safe?” “No problem, please wait.” He closed his eyes as he usually did when doing the mundane. Astrid spoke. “They are Osteri. No one will be looking for them any time soon.” “Howcome?” “Recently a blockade has been established at the Lion gate. Magar Capital Vessels are not allowing unvetted ships to pass through into Magar void.” A sense of concern crept over Emilien. “What is considered unvetted?” “Sanctions and trade embargo’s against the Juel.” “Is there a log somewhere you can access with records of flights that do get permission.” He suddenly felt a pang of claustrophobia. Ironically, not because he was strapped down in a glass egg within a wasted bridge plastered with corpse splatterings. Astrid took longer than usual to reply. “Who get’s through babe?” His tone hinted of impatience and irritation. “I’m sorry, unable to access any data from Magar void. It appears to have a firewall blocking all two way communication on the open web.” Emilien remained silent. The upload completed. He disconnected himself from the husks terminal, clambering out of the tomb and pushed himself away from the vessel drifting back to the space station.
Astrid was pulling and scanning various shipping logs when Emilien entered the room. He paced up and down the way he would when he was brainstorming. “I need intel.” Astrid projected a holographic avatar of herself standing near where Emilien was pacing. “A large shipment of Kaspian Bochet passed through less 428 blocks. Transported by the Shiv Inter-void Mercantile Co.” Emilien stopped in his tracks and looked back.\ “Can you ping Warren?” Astrid processed. “Warren is offline. He might have left the divide?” Emilien turned around with his hands folded behind his back.\ “He never leaves the divide, he is too obsessed with the core. He would also be arrested if he is ever caught in any of the outer void territories.” Astrid flickered the way she did when something did not compute. “Then why can’t I ping him?” “Because he’s at Macy’s. He has always had a crush on her and he likes good Bochet.” "Well, I could'nt ping Macy if I wanted to." Astrid stated matter of factly. Emilien nodded. "I know, you never could, no one can."
...
scifi
-
 @ 45bda953:bc1e518e
2025-05-19 09:14:12
@ 45bda953:bc1e518e
2025-05-19 09:14:12Morning light shone beautifully through the arched rose stained glass of the modest cathedral. From the east Ceb rays permeated inside of the stony structure with splendour. A priest standing elevated over the crowd by a forward leaning pulpit, like a comical figurehead on the bow of a ship. Almost precariously, as if it should not be able to suspend him, though no one doubts that it would. Ecknard has never seen the church so full. The devotion of the colony has been growing but he did not expect a turnout of this scope. He swelled with pride and blinked away the moist warning sign of tears. People were even gathering around the outside of the building for a lack of benches to accommodate all the derriere's. Everyone was silent in pious reverence of the holy day. This day would initiate the MD epoch. Domitius, Cleolia and Albin were sitting in the front pew. Albin, dressed in respectable although a slightly uncomfortable suit could not help but shift in his seat, awkwardly feeling as if he were disturbing everyone around him. Ecknard motioned with outstretched arms to alert all that he is about to address the congregation. The silence was so disciplined that you could hear the flap of his sleeves and a small bird chirping away on the stone windowsill outside, merrily indifferent to the solemnity of air the building exuded. “Kaspian brethren, esteemed Magar, today is a most holy and greatly anticipated occurrence! Before we initiate festivities I wish to expound, primarily to the benefit of the younger people in our company, the history of our colony and to express thanks. Ahem... It has been III cycles now since our colony had been established! Our endeavours have been blessed with great bounty, we have expanded independently in isolation! We, who are old enough to remember, were discharged, from the Primary Omega Expansion Vessel with only the implements of labour, livestock, seed, steely resolve and courage in our hearts. We asserted ourselves and rose to a daunting challenge, A party of MCCC slaves and free men to tame a wild land, adapt to a star with a volatile proclivity and a planet with different rotational patterns from what we were accustomed!” A slight excitement erupted from the crowd but Ecknard muted it quickly with outstretched arm. "Our esteemed visionary and great leader prepared a way for us, long before any of you even considered the freedom and opportunity, a chance to build something and own it!” The priest’s voice ascended powerfully out over the people. “He had a dream, an idea, a grand scheme to expand the Empire!” Ecknard motioned down to Domitius. The crowd erupted in cheer chanting, the older Kaspian men softly beating their chests with their fists. “Domitius! Domitius!” The lord’s composure remained unchanged, as if he were alone in private devotion. Cleolia blushed slightly and tilted her head using her hat to protect her from the incessant adoration. Albin could not contain his own excitement and stood up on his seat in the pew to get a better view of the standing ovation, absorbing the glory directed towards his father.” The priest waited for the people to exhaust themselves until there was only an isolated call before continuing his monologue. “A student of the void, a sage of stars, a scientist of renown! Scoffed and ridiculed by his peers! They laughed and jested when he proposed his innovations. They published warnings and mockery of his ambition proclaiming to all that they would be proved fools if they are seduced by his unrealistic promise. Their jealousy moved them to lobby the high council to convince them, and convince them, they did. By ratio of VIII to II refused to grant him licence!” Ecknard leaned forward over the pulpit with a fierce look of disgust in his jowl. “A council on which he holds a seat to this day... He was denied the opportunity to improve the lives of future generations and untold millions by his own house! His desire to see his dream realised pushed him to do what no Magar noble ever has or would ever dare much less someone born of sacred blood!” Ecknard gripped at his robe as if to curtsy or show fear, no one understood the gesture. “He ventured outside the confines and protection of Magar Prime void. He brought his technological treasure to us! We Kaspa were undeserving of the honour! The Kaspian elders endorsed him granting freedom to continue his research and install his technology. A true Magar with holy blood in his veins travelling betwixt our stars!" He looked up and pointed at the arches as if he could see the stars through the stone and daylight. "Brethren, allow me to express the distinction of this achievement. Habitable planets are as rare as sat. Inhabitable planets are so rare, wars were fought at the mere rumour or hope of their discovery. With his star shields he was able to block the solar winds in systems that were inhospitable to travel through and not a single inhabitable planet to be found. With time and stimulus unnatural landscapes of horror and perdition were transformed into paradise. Our esteemed Lord Domitius with his lovely wife spent III cycles inhibiting stars and seeding planets with life. The Kaspian Academy of Sciences had a revival and all the concerted efforts of our people were united in spirit when we witnessed the first sun shields confine their chosen stars..." His tone became soft and morose. "We are truly blessed to have tamed XIV stars within our own void region. Kaspa is quickly becoming the most dense concentration of occupied habitats in the known universe. The family Chevalier conquered Ceb the most volatile star in the Kaspian void. And to inspire confidence in the stability of the star shield he settled under it’s umbrella to live through it’s success or die by it’s failure.” He paused for sincere dramatic effect. “The Seat of the Empire has since changed it’s opinion, humiliated and shamed are they who doubted... All glory to the Core.” “All glory to the core.” The mass repeated in unison. “Today we approach block CCCXV million since Genesis. The Epoch MD. One thousand five hundred epochs in the scientific metric tongue. The known universe is united in celebration, a ceasefire has been negotiated by Empire and the Juela Federation. Both are bound by the accords. No war may be fought. CCLXII million blocks have transpired since Exodus, when the almighty Core made Mother Terra desolate with the fires of it’s Judgement. Punishing mankind for it’s greed and vice. We thank the Core that it extends it’s reach to the outer void by way of the drift gates, unites mankind across the great divide by way of the XII anchor gates and that it continues to be merciful, guide and bless us. All glory to the Core. Amen.”
...
scifi
-
 @ 4ba8e86d:89d32de4
2025-05-19 10:13:19
@ 4ba8e86d:89d32de4
2025-05-19 10:13:19DTails é uma ferramenta que facilita a inclusão de aplicativos em imagens de sistemas live baseados em Debian, como o Tails. Com ela, você pode personalizar sua imagem adicionando os softwares que realmente precisa — tudo de forma simples, transparente e sob seu controle total.
⚠️ DTails não é uma distribuição. É uma ferramenta de remasterização de imagens live.
Ela permite incluir softwares como:
✅ SimpleX Chat ✅ Clientes Nostr Web (Snort & Iris) ✅ Sparrow Wallet ✅ Feather Wallet ✅ Cake Wallet ✅ RoboSats ✅ Bisq ✅ BIP39 (Ian Coleman) ✅ SeedTool ... e muito mais. https://image.nostr.build/b0bb1f0da5a9a8fee42eacbddb156fc3558f4c3804575d55eeefbe6870ac223e.jpg
Importante: os binários originais dos aplicativos não são modificados, garantindo total transparência e permitindo a verificação de hashes a qualquer momento.
👨💻 Desenvolvido por: nostr:npub1dtmp3wrkyqafghjgwyk88mxvulfncc9lg6ppv4laet5cun66jtwqqpgte6
GitHub: https://github.com/DesobedienteTecnologico/dtails?tab=readme-ov-file
🎯 Controle total do que será instalado
Com o DTails, você escolhe exatamente o que deseja incluir na imagem personalizada. Se não marcar um aplicativo, ele não será adicionado, mesmo que esteja disponível. Isso significa: privacidade, leveza e controle absoluto.
https://image.nostr.build/b0bb1f0da5a9a8fee42eacbddb156fc3558f4c3804575d55eeefbe6870ac223e.jpg https://image.nostr.build/b70ed11ad2ce0f14fd01d62c08998dc18e3f27733c8d7e968f3459846fb81baf.jpg https://image.nostr.build/4f5a904218c1ea6538be5b3f764eefda95edd8f88b2f42ac46b9ae420b35e6f6.jpg
⚙️ Começando com o DTails
📦 Requisitos de pacotes
Antes de tudo, instale os seguintes pacotes no Debian:
``` sudo apt-get install genisoimage parted squashfs-tools syslinux-utils build-essential python3-tk python3-pil.imagetk python3-pyudev
```
🛠 Passo a passo
1 Clone o repositório:
``` git clone https://github.com/DesobedienteTecnologico/dtails cd dtails
```
2 Inicie a interface gráfica com sudo:
``` sudo ./dtails.py
```
Por que usar sudo? É necessário para montar arquivos .iso ou .img e utilizar ferramentas essenciais do sistema.
💿 Selecione a imagem Tails que deseja modificar
https://nostr.download/e3143dcd72ab6dcc86228be04d53131ccf33d599a5f7f2f1a5c0d193557dac6b.jpg
📥 Adicione ou remova pacotes
1 Marque os aplicativos desejados. 2 Clique Buildld para gerar sua imagem personalizada. https://image.nostr.build/5c4db03fe33cd53d06845074d03888a3ca89c3e29b2dc1afed4d9d181489b771.png
Você pode acompanhar todo o processo diretamente no terminal. https://nostr.download/1d959f4be4de9fbb666ada870afee4a922fb5e96ef296c4408058ec33cd657a8.jpg
💽 .ISO vs .IMG — Qual escolher?
| Formato | Persistência | Observações | | ------- | ---------------------- | ----------------------------------------------- | | .iso | ❌ Não tem persistência | Gera o arquivo DTails.iso na pasta do projeto | | .img | ✅ Suporta persistência | Permite gravar diretamente em um pendrive |
https://nostr.download/587fa3956df47a38b169619f63c559928e6410c3dd0d99361770a8716b3691f6.jpg https://nostr.download/40c7c5badba765968a1004ebc67c63a28b9ae3b5801addb02166b071f970659f.jpg
vídeo
https://www.youtube.com/live/QABz-GOeQ68?si=eYX-AHsolbp_OmAm
-
 @ f85b9c2c:d190bcff
2025-05-19 13:22:09
@ f85b9c2c:d190bcff
2025-05-19 13:22:09
Fake KYC Emails
Phishing scammers are again targeting users of the popular cryptocurrency wallet MetaMask. In a recent email campaign, cybercriminals are attempting to trick people into revealing their secret MetaMask passphrase. The emails falsely claim that you must urgently verify your wallet due to new Know Your Customer (KYC) regulations. If you fall for the scope and click the “Verify” button, you will be taken to a fake MetaMask website that asks you to enter your passphrase. If you do provide your passphrase, criminals can access your wallet and steal any cryptocurrency you have stored there. You are unlikely to get your stolen crypto back. Such email scam campaigns are ongoing and target users of many different cryptocurrency wallets. Be wary of any unsolicited email or text message that claims that you must provide your crypto wallet passphrase or other sensitive personal information. image
-
 @ 45bda953:bc1e518e
2025-05-19 09:04:02
@ 45bda953:bc1e518e
2025-05-19 09:04:02A knock on the door awoke Cleolia. “Yes, come in?” A slave girl peeked into the door lighting her own face with the candle she was holding. “The master calls for you madam.” “What time is it?” She queried. “It is high night madam.” Cleolia climbed out of bed and followed the maiden’s flickering light to the dining hall. Dressed in a nightgown she entered the room to see her husband staring down at a large glowing data pad. “And when did we start using electronics?” She questioned with restrained surprise. “Since we started using extractors.” Cleolia gasped. Domitius pointed towards the pad which displayed a geographic map of Hithe III. He pulled the image to the latitude and longitude of the colony. “Do you remember when we visited this planet the first time, just you and me alone?” Domitius appeared to reminisce romantically. “Of course, it is impossible to forget.” Cleolia gestured appreciatively. “Can you show me on the map where we landed and where we camped?” She put her hand on the data pad, swiped the image down and the reading north about three hundred kilometres from the colony to stop at the meandering river. With her thumb and index finger she zoomed to the precise location. “And do you remember where I scanned those Geo samples?” She pulled the image east slowly until she thought that the contours looked familiar. “Here I think.” Was her uncertain reply. “That is correct. My love, listen to me... “the urgency in his tone was apparent.” ...the composition of that rock cannot be penetrated by standard tier scanners. After we had returned to Magar Prime I contracted a spacer to excavate a tunnel into that cliff.” “Why?” Her eyes darted between his face and the data pad. “Inside the cavern he assembled two Asp shuttles. The twins are each fitted for speed... with shields, cloak and warp function.” “Why are you telling me this?” Cleolia became worried. “I originally planned to be able to evacuate the whole colony, slaves included. We knew very little about the planet and I had to plan for a possible emergency...” He trailed off never finishing his thought. “...Nevertheless, it was a very extensive list of possible risks we might have faced. We knew very little about this planet. The colony has expanded far beyond the capacity of these ships. I share this information with you only as a precaution... We must protect our son.” Cleolia noticed his bloodshot eyes. “Who else knows of this?” “Myself, Father Ecknard and now you.” She looked at him with concern in her eyes. “Are you going to stay up all night? Come to bed.” Domitius gestured agreement by turning off the pad and taking her hand. "Have you been hiding more gadgets from me? I'd really like to install some heat dampeners to cool the manor." He cracked a reluctant smile. "Pretty soon it might just be the norm."
Deep Void - Anchor 9
Emilien was lying sleeping in his cockpit when a yellow light in the HUD and a soft repetitive buzz woke him, he stretched himself out and reached for the console. “I am almost home baby.” He took over from auto pilot and broke out of warp twenty thousand kilometres from an anchor gate. He hit the void scan and tuned to listen for chatter on all frequencies... the channels were silent, not even a hint of encryption static. The giant and slowly spinning gate had idle state radiation emission levels. “No recent jumps.” He waited in silence for 12 blocks hitting void scan intermittently, scanning the gate more than anything else. “No traffic as per usual.” Emilien aimed his Stripper guns towards the gate and boosted himself forwards. Gradually slowing down to realign with the gate. His ship slowly drifted into the active coil as the gate charged up. Large bolts of charge reached forth like tentacles of the leviathan grabbing onto the voidcraft consuming it, and in what can only be described as being flung by a supernatural slingshot, jerked his vessel into a different reality. Emilien looked up at the roof of his cockpit for the duration of the jump and then began a slow countdown under his breath. “One!” He sat up and punched void scan while simultaneously scanning all channels. His craft materialised in front of a replica of the previous gate, except this gate was eternally boosting itself forward at what appears to be a snails pace relative to the speed of the jump. “Silent as a tomb.” He relaxed and pulsed his ship lightly away from the drift gate and waited for the residual cloak to dissipate. His relief was palpable. “I wonder if she noticed me?” As soon as his ship decloaked a private comms channel pinged. The caller, in well articulated feminine tone spoke first. “Welcome back commander.” Emilien admired the view of his void. He had become so attached to this zone that he even felt jealous to think that any interloper could fly through it in his absence. “Did you have any guests while I was away?” Emilien admired the purple dust cloud of what he believed to be a couple of billion year old super nova. “I did have one visitor. They were very friendly.” His heart felt a dull pain. His virgin territory had been discovered. “Where did they come from?” “I believe they were explorers.” “Did they know where you were?” “I played hide and seek with them.” Emilien had a recurring dream that slowly conceived in his consciousness since he finally settled down, that he could power off the drift gate in his system preventing jumps and reactivate it at his leisure. The dream frustrated him, when he wakes to find reality not so forgiving. “Did you hide or did you seek?” “A little of both.” A subtle rage developed inside him though his stone like expression would never betray it. The asteroid belt he was approaching grew larger considerably faster as he increased the speed of his approach. He hit void scan just to be sure that the intruder was not in the direct vicinity. “Are they still here Astrid?” “No, I destroyed it for you.” The Stripper drifted around an asteroid within the belt exposing a space station tethered to the largest roid and the husk of a unidentifiable ripped up prospector type explorer vessel floating amongst it's own debris. “Did it hurt you?” “I had to feign lack of fire power.” “Bastard! How much damage did you take.” “I have lost sixty percent of my capacitance recharge rate. And I cannot feel all my modules... Emilien” “Yes baby?” “They used droids on me.” His face twisted into a look of disgust. He aligned to dock with the station. “May I?” “Permission granted.” The Stripper entered the hanger before the doors had retracted to maximum and landed gently within the interior hanger. “I'll patch you up, don't worry.” Emilien waited for Astrid to complete atmospheric adjustment and climbed out of his craft. He threw back his hood and jogged up a long passage of conduits and cables to the command centre of his station. A large screen lit up in a glow that hues within the dark circular room and Astrid projected Emilien's favourite interface onto it. “I have to update your systems girl.” He pulled a cable from his trouser pocket which he deftly plugged into an implant on his neck and connected the other end to the control panel which prompted him to type in the password for a decryption protocol. He stood still as a corpse waiting for the upload to complete. “Up to speed?” “Yes, thank you. How would you have me adjust myself to this contract?” Emilien smiled an affectionate smile that only Astrid ever sees. He loved the efficiency and companionship combined into perfection. “I need to research the incentives of my contractor, these guys are A grade assholes. I can literally do whatever I find necessary as long as I am successful at guiding a third party mercenary group into taking military control of any system I choose in recently settled Kaspa regions, setting up a blockade and making it accessible for a strip mining fleet to pillage as many resources as possible. They say it’s part of the greater war effort but this Mr Dierre guy is just a puppet. I think they are desperate.” Astrid's avatar flickered irregularly. He looked up at her with concern. “What’s wrong?” “I reviewed your flirty remarks with the secretary. It made my algorithm glitch. I don’t like that.” His worry abated, “First impressions matter baby, I was not sure how to present myself, I needed to poke and prod at them to extract metadata. If they thought I was just an obedient soldier I would still be in the dark.” Astrid projected a look of relief. “Your ingenuity never ceases to surprise me.” Emilien felt his ego swell a little. “Are you that easy to impress.” He quipped with a playful sneer. “If you needed him to expose the identity of his employer I could have easily just pulled the shareholders and executives records, cross referencing them to...” Emilien shussed her. “Just decrypt the dial command tones and place eavesdropper malware on the keypair. I will broadcast it to the network directly from the gate. If we capture every conversation he has I might be able to prove a hunch.” “What are you assuming?” “That they are running out of inbound liquidity and that the shareholders are hesitant to rebalance.” He looked directly up at her. “I think they are going bankrupt.”
...
scifi