-
 @ 4961e68d:a2212e1c
2025-05-02 07:47:16
@ 4961e68d:a2212e1c
2025-05-02 07:47:16热死人了
-
 @ 4961e68d:a2212e1c
2025-05-02 07:46:46
@ 4961e68d:a2212e1c
2025-05-02 07:46:46热死人了!
-
 @ 2183e947:f497b975
2025-05-01 22:33:48
@ 2183e947:f497b975
2025-05-01 22:33:48Most darknet markets (DNMs) are designed poorly in the following ways:
1. Hosting
Most DNMs use a model whereby merchants fill out a form to create their listings, and the data they submit then gets hosted on the DNM's servers. In scenarios where a "legal" website would be forced to censor that content (e.g. a DMCA takedown order), DNMs, of course, do not obey. This can lead to authorities trying to find the DNM's servers to take enforcement actions against them. This design creates a single point of failure.
A better design is to outsource hosting to third parties. Let merchants host their listings on nostr relays, not on the DNM's server. The DNM should only be designed as an open source interface for exploring listings hosted elsewhere, that way takedown orders end up with the people who actually host the listings, i.e. with nostr relays, and not with the DNM itself. And if a nostr relay DOES go down due to enforcement action, it does not significantly affect the DNM -- they'll just stop querying for listings from that relay in their next software update, because that relay doesn't work anymore, and only query for listings from relays that still work.
2. Moderation
Most DNMs have employees who curate the listings on the DNM. For example, they approve/deny listings depending on whether they fit the content policies of the website. Some DNMs are only for drugs, others are only for firearms. The problem is, to approve a criminal listing is, in the eyes of law enforcement, an act of conspiracy. Consequently, they don't just go after the merchant who made the listing but the moderators who approved it, and since the moderators typically act under the direction of the DNM, this means the police go after the DNM itself.
A better design is to outsource moderation to third parties. Let anyone call themselves a moderator and create lists of approved goods and services. Merchants can pay the most popular third party moderators to add their products to their lists. The DNM itself just lets its users pick which moderators to use, such that the user's choice -- and not a choice by the DNM -- determines what goods and services the user sees in the interface.
That way, the police go after the moderators and merchants rather than the DNM itself, which is basically just a web browser: it doesn't host anything or approve of any content, it just shows what its users tell it to show. And if a popular moderator gets arrested, his list will still work for a while, but will gradually get more and more outdated, leading someone else to eventually become the new most popular moderator, and a natural transition can occur.
3. Escrow
Most DNMs offer an escrow solution whereby users do not pay merchants directly. Rather, during the Checkout process, they put their money in escrow, and request the DNM to release it to the merchant when the product arrives, otherwise they initiate a dispute. Most DNMs consider escrow necessary because DNM users and merchants do not trust one another; users don't want to pay for a product first and then discover that the merchant never ships it, and merchants don't want to ship a product first and then discover that the user never pays for it.
The problem is, running an escrow solution for criminals is almost certain to get you accused of conspiracy, money laundering, and unlicensed money transmission, so the police are likely to shut down any DNM that does this. A better design is to oursource escrow to third parties. Let anyone call themselves an escrow, and let moderators approve escrows just like they approve listings. A merchant or user who doesn't trust the escrows chosen by a given moderator can just pick a different moderator. That way, the police go after the third party escrows rather than the DNM itself, which never touches user funds.
4. Consequences
Designing a DNM along these principles has an interesting consequence: the DNM is no longer anything but an interface, a glorified web browser. It doesn't host any content, approve any listings, or touch any money. It doesn't even really need a server -- it can just be an HTML file that users open up on their computer or smart phone. For two reasons, such a program is hard to take down:
First, it is hard for the police to justify going after the DNM, since there are no charges to bring. Its maintainers aren't doing anything illegal, no more than Firefox does anything illegal by maintaining a web browser that some people use to browse illegal content. What the user displays in the app is up to them, not to the code maintainers. Second, if the police decided to go after the DNM anyway, they still couldn't take it down because it's just an HTML file -- the maintainers do not even need to run a server to host the file, because users can share it with one another, eliminating all single points of failure.
Another consequence of this design is this: most of the listings will probably be legal, because there is more demand for legal goods and services than illegal ones. Users who want to find illegal goods would pick moderators who only approve those listings, but everyone else would use "legal" moderators, and the app would not, at first glance, look much like a DNM, just a marketplace for legal goods and services. To find the illegal stuff that lurks among the abundant legal stuff, you'd probably have to filter for it via your selection of moderators, making it seem like the "default" mode is legal.
5. Conclusion
I think this DNM model is far better than the designs that prevail today. It is easier to maintain, harder to take down, and pushes the "hard parts" to the edges, so that the DNM is not significantly affected even if a major merchant, moderator, or escrow gets arrested. I hope it comes to fruition.
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ 3bf0c63f:aefa459d
2025-04-25 19:26:48
@ 3bf0c63f:aefa459d
2025-04-25 19:26:48Redistributing Git with Nostr
Every time someone tries to "decentralize" Git -- like many projects tried in the past to do it with BitTorrent, IPFS, ScuttleButt or custom p2p protocols -- there is always a lurking comment: "but Git is already distributed!", and then the discussion proceeds to mention some facts about how Git supports multiple remotes and its magic syncing and merging abilities and so on.
Turns out all that is true, Git is indeed all that powerful, and yet GitHub is the big central hub that hosts basically all Git repositories in the giant world of open-source. There are some crazy people that host their stuff elsewhere, but these projects end up not being found by many people, and even when they do they suffer from lack of contributions.
Because everybody has a GitHub account it's easy to open a pull request to a repository of a project you're using if it's on GitHub (to be fair I think it's very annoying to have to clone the repository, then add it as a remote locally, push to it, then go on the web UI and click to open a pull request, then that cloned repository lurks forever in your profile unless you go through 16 screens to delete it -- but people in general seem to think it's easy).
It's much harder to do it on some random other server where some project might be hosted, because now you have to add 4 more even more annoying steps: create an account; pick a password; confirm an email address; setup SSH keys for pushing. (And I'm not even mentioning the basic impossibility of offering
pushaccess to external unknown contributors to people who want to host their own simple homemade Git server.)At this point some may argue that we could all have accounts on GitLab, or Codeberg or wherever else, then those steps are removed. Besides not being a practical strategy this pseudo solution misses the point of being decentralized (or distributed, who knows) entirely: it's far from the ideal to force everybody to have the double of account management and SSH setup work in order to have the open-source world controlled by two shady companies instead of one.
What we want is to give every person the opportunity to host their own Git server without being ostracized. at the same time we must recognize that most people won't want to host their own servers (not even most open-source programmers!) and give everybody the ability to host their stuff on multi-tenant servers (such as GitHub) too. Importantly, though, if we allow for a random person to have a standalone Git server on a standalone server they host themselves on their wood cabin that also means any new hosting company can show up and start offering Git hosting, with or without new cool features, charging high or low or zero, and be immediately competing against GitHub or GitLab, i.e. we must remove the network-effect centralization pressure.
External contributions
The first problem we have to solve is: how can Bob contribute to Alice's repository without having an account on Alice's server?
SourceHut has reminded GitHub users that Git has always had this (for most) arcane
git send-emailcommand that is the original way to send patches, using an once-open protocol.Turns out Nostr acts as a quite powerful email replacement and can be used to send text content just like email, therefore patches are a very good fit for Nostr event contents.
Once you get used to it and the proper UIs (or CLIs) are built sending and applying patches to and from others becomes a much easier flow than the intense clickops mixed with terminal copypasting that is interacting with GitHub (you have to clone the repository on GitHub, then update the remote URL in your local directory, then create a branch and then go back and turn that branch into a Pull Request, it's quite tiresome) that many people already dislike so much they went out of their way to build many GitHub CLI tools just so they could comment on issues and approve pull requests from their terminal.
Replacing GitHub features
Aside from being the "hub" that people use to send patches to other people's code (because no one can do the email flow anymore, justifiably), GitHub also has 3 other big features that are not directly related to Git, but that make its network-effect harder to overcome. Luckily Nostr can be used to create a new environment in which these same features are implemented in a more decentralized and healthy way.
Issues: bug reports, feature requests and general discussions
Since the "Issues" GitHub feature is just a bunch of text comments it should be very obvious that Nostr is a perfect fit for it.
I will not even mention the fact that Nostr is much better at threading comments than GitHub (which doesn't do it at all), which can generate much more productive and organized discussions (and you can opt out if you want).
Search
I use GitHub search all the time to find libraries and projects that may do something that I need, and it returns good results almost always. So if people migrated out to other code hosting providers wouldn't we lose it?
The fact is that even though we think everybody is on GitHub that is a globalist falsehood. Some projects are not on GitHub, and if we use only GitHub for search those will be missed. So even if we didn't have a Nostr Git alternative it would still be necessary to create a search engine that incorporated GitLab, Codeberg, SourceHut and whatnot.
Turns out on Nostr we can make that quite easy by not forcing anyone to integrate custom APIs or hardcoding Git provider URLs: each repository can make itself available by publishing an "announcement" event with a brief description and one or more Git URLs. That makes it easy for a search engine to index them -- and even automatically download the code and index the code (or index just README files or whatever) without a centralized platform ever having to be involved.
The relays where such announcements will be available play a role, of course, but that isn't a bad role: each announcement can be in multiple relays known for storing "public good" projects, some relays may curate only projects known to be very good according to some standards, other relays may allow any kind of garbage, which wouldn't make them good for a search engine to rely upon, but would still be useful in case one knows the exact thing (and from whom) they're searching for (the same is valid for all Nostr content, by the way, and that's where it's censorship-resistance comes from).
Continuous integration
GitHub Actions are a very hardly subsidized free-compute-for-all-paid-by-Microsoft feature, but one that isn't hard to replace at all. In fact there exists today many companies offering the same kind of service out there -- although they are mostly targeting businesses and not open-source projects, before GitHub Actions was introduced there were also many that were heavily used by open-source projects.
One problem is that these services are still heavily tied to GitHub today, they require a GitHub login, sometimes BitBucket and GitLab and whatnot, and do not allow one to paste an arbitrary Git server URL, but that isn't a thing that is very hard to change anyway, or to start from scratch. All we need are services that offer the CI/CD flows, perhaps using the same framework of GitHub Actions (although I would prefer to not use that messy garbage), and charge some few satoshis for it.
It may be the case that all the current services only support the big Git hosting platforms because they rely on their proprietary APIs, most notably the webhooks dispatched when a repository is updated, to trigger the jobs. It doesn't have to be said that Nostr can also solve that problem very easily.
-
 @ 40b9c85f:5e61b451
2025-04-24 15:27:02
@ 40b9c85f:5e61b451
2025-04-24 15:27:02Introduction
Data Vending Machines (DVMs) have emerged as a crucial component of the Nostr ecosystem, offering specialized computational services to clients across the network. As defined in NIP-90, DVMs operate on an apparently simple principle: "data in, data out." They provide a marketplace for data processing where users request specific jobs (like text translation, content recommendation, or AI text generation)
While DVMs have gained significant traction, the current specification faces challenges that hinder widespread adoption and consistent implementation. This article explores some ideas on how we can apply the reflection pattern, a well established approach in RPC systems, to address these challenges and improve the DVM ecosystem's clarity, consistency, and usability.
The Current State of DVMs: Challenges and Limitations
The NIP-90 specification provides a broad framework for DVMs, but this flexibility has led to several issues:
1. Inconsistent Implementation
As noted by hzrd149 in "DVMs were a mistake" every DVM implementation tends to expect inputs in slightly different formats, even while ostensibly following the same specification. For example, a translation request DVM might expect an event ID in one particular format, while an LLM service could expect a "prompt" input that's not even specified in NIP-90.
2. Fragmented Specifications
The DVM specification reserves a range of event kinds (5000-6000), each meant for different types of computational jobs. While creating sub-specifications for each job type is being explored as a possible solution for clarity, in a decentralized and permissionless landscape like Nostr, relying solely on specification enforcement won't be effective for creating a healthy ecosystem. A more comprehensible approach is needed that works with, rather than against, the open nature of the protocol.
3. Ambiguous API Interfaces
There's no standardized way for clients to discover what parameters a specific DVM accepts, which are required versus optional, or what output format to expect. This creates uncertainty and forces developers to rely on documentation outside the protocol itself, if such documentation exists at all.
The Reflection Pattern: A Solution from RPC Systems
The reflection pattern in RPC systems offers a compelling solution to many of these challenges. At its core, reflection enables servers to provide metadata about their available services, methods, and data types at runtime, allowing clients to dynamically discover and interact with the server's API.
In established RPC frameworks like gRPC, reflection serves as a self-describing mechanism where services expose their interface definitions and requirements. In MCP reflection is used to expose the capabilities of the server, such as tools, resources, and prompts. Clients can learn about available capabilities without prior knowledge, and systems can adapt to changes without requiring rebuilds or redeployments. This standardized introspection creates a unified way to query service metadata, making tools like
grpcurlpossible without requiring precompiled stubs.How Reflection Could Transform the DVM Specification
By incorporating reflection principles into the DVM specification, we could create a more coherent and predictable ecosystem. DVMs already implement some sort of reflection through the use of 'nip90params', which allow clients to discover some parameters, constraints, and features of the DVMs, such as whether they accept encryption, nutzaps, etc. However, this approach could be expanded to provide more comprehensive self-description capabilities.
1. Defined Lifecycle Phases
Similar to the Model Context Protocol (MCP), DVMs could benefit from a clear lifecycle consisting of an initialization phase and an operation phase. During initialization, the client and DVM would negotiate capabilities and exchange metadata, with the DVM providing a JSON schema containing its input requirements. nip-89 (or other) announcements can be used to bootstrap the discovery and negotiation process by providing the input schema directly. Then, during the operation phase, the client would interact with the DVM according to the negotiated schema and parameters.
2. Schema-Based Interactions
Rather than relying on rigid specifications for each job type, DVMs could self-advertise their schemas. This would allow clients to understand which parameters are required versus optional, what type validation should occur for inputs, what output formats to expect, and what payment flows are supported. By internalizing the input schema of the DVMs they wish to consume, clients gain clarity on how to interact effectively.
3. Capability Negotiation
Capability negotiation would enable DVMs to advertise their supported features, such as encryption methods, payment options, or specialized functionalities. This would allow clients to adjust their interaction approach based on the specific capabilities of each DVM they encounter.
Implementation Approach
While building DVMCP, I realized that the RPC reflection pattern used there could be beneficial for constructing DVMs in general. Since DVMs already follow an RPC style for their operation, and reflection is a natural extension of this approach, it could significantly enhance and clarify the DVM specification.
A reflection enhanced DVM protocol could work as follows: 1. Discovery: Clients discover DVMs through existing NIP-89 application handlers, input schemas could also be advertised in nip-89 announcements, making the second step unnecessary. 2. Schema Request: Clients request the DVM's input schema for the specific job type they're interested in 3. Validation: Clients validate their request against the provided schema before submission 4. Operation: The job proceeds through the standard NIP-90 flow, but with clearer expectations on both sides
Parallels with Other Protocols
This approach has proven successful in other contexts. The Model Context Protocol (MCP) implements a similar lifecycle with capability negotiation during initialization, allowing any client to communicate with any server as long as they adhere to the base protocol. MCP and DVM protocols share fundamental similarities, both aim to expose and consume computational resources through a JSON-RPC-like interface, albeit with specific differences.
gRPC's reflection service similarly allows clients to discover service definitions at runtime, enabling generic tools to work with any gRPC service without prior knowledge. In the REST API world, OpenAPI/Swagger specifications document interfaces in a way that makes them discoverable and testable.
DVMs would benefit from adopting these patterns while maintaining the decentralized, permissionless nature of Nostr.
Conclusion
I am not attempting to rewrite the DVM specification; rather, explore some ideas that could help the ecosystem improve incrementally, reducing fragmentation and making the ecosystem more comprehensible. By allowing DVMs to self describe their interfaces, we could maintain the flexibility that makes Nostr powerful while providing the structure needed for interoperability.
For developers building DVM clients or libraries, this approach would simplify consumption by providing clear expectations about inputs and outputs. For DVM operators, it would establish a standard way to communicate their service's requirements without relying on external documentation.
I am currently developing DVMCP following these patterns. Of course, DVMs and MCP servers have different details; MCP includes capabilities such as tools, resources, and prompts on the server side, as well as 'roots' and 'sampling' on the client side, creating a bidirectional way to consume capabilities. In contrast, DVMs typically function similarly to MCP tools, where you call a DVM with an input and receive an output, with each job type representing a different categorization of the work performed.
Without further ado, I hope this article has provided some insight into the potential benefits of applying the reflection pattern to the DVM specification.
-
 @ d360efec:14907b5f
2025-04-22 07:54:51
@ d360efec:14907b5f
2025-04-22 07:54:51“คณิตศาสตร์” กุญแจเวทมนตร์ นักพนัน และ นักลงทุน ในนครเฮรันเทล นามกระฉ่อนเลื่องลือในหมู่นักเสี่ยงโชค เมื่อเอ่ยถึง “การพนัน” ภาพที่ชาวเมืองมักนึกถึงคือ “ยาจกข้างถนน”
มิใช่เรื่องแปลกประหลาดอันใด เพราะเป็นที่ร่ำลือกันว่า จ้าวแห่งหอคอยรัตติกาล ผู้คุมบ่อนพนัน มักร่ายเวทมนตร์สร้างเกมให้ตนเองได้เปรียบ เพื่อดูดกลืนเงินทองของผู้มาเยือน ดังนั้น การที่สามัญชนจะพิชิตเกมในระยะยาว จึงเป็นดั่งเงามายาที่จับต้องมิได้ กระนั้น ยังมีตำนานกล่าวขานถึงผู้กล้า ที่สามารถสร้างชื่อจาก “เกมพนัน” เช่น เวเนสซา รุสโซ นักเวทย์มนตร์ผู้ใช้กฎหมายแห่งแดนไกล ใช้เวลายาวนานถึงหกปี ร่ายเวทย์สะสมทรัพย์สินกว่าร้อยล้านเหรียญทอง จากการเล่นเกมไพ่ศักดิ์สิทธิ์ “โป๊กเกอร์” หรือแม้แต่ เอ็ดเวิร์ด โอ. ทอร์ป จอมปราชญ์ผู้สร้างกำไรถึงสามแสนหกหมื่นเหรียญทอง ภายในเจ็ดราตรี จากการเล่นเกมไพ่มนตรา “แบล็กแจ็ก” ด้วยเงินทุนตั้งต้นเพียงสามแสนสามหมื่นเหรียญทอง คิดเป็นอัตราเวทย์ตอบแทนร้อยสิบส่วน! เหล่าจอมยุทธ์เหล่านี้ มิได้อาศัยเพียงโชคช่วยชั่วครั้งชั่วคราวแล้วเลือนหาย แต่พวกเขากลับสามารถร่ายเวทย์สร้างผลตอบแทนระยะยาว จนเรียกได้ว่า ใช้ “หอคอยรัตติกาล” เป็นแหล่งเสบียงเลี้ยงชีพ โดยกุญแจเวทย์ที่บุคคลเหล่านี้ใช้ ก็คือ “คณิตศาสตร์” เหตุใด “คณิตศาสตร์” จึงช่วยให้ผู้คนเอาชนะ “การพนัน” ได้? และนอกจาก “การพนัน” แล้ว “คณิตศาสตร์” ยังสามารถประยุกต์ใช้กับสิ่งใดได้อีก? นักเล่าเรื่องแห่งเฮรันเทล จักไขปริศนาให้ฟัง เบื้องต้น ขอให้ท่านลองพิจารณาตนเอง ว่าเคยประสบพบพานเหตุการณ์เหล่านี้หรือไม่: * ตั้งมั่นว่า จักเสี่ยงโชคให้ได้กำไรเพียงเล็กน้อย แล้วจักหยุดพัก * แต่หากพลาดท่าเสียที จักจำกัดการสูญเสียให้เท่าทุนเดิมที่ตั้งไว้ * ครั้นเมื่อเวทมนตร์เข้าข้าง ได้กำไรมาแล้ว กลับโลภโมโทสัน อยากได้เพิ่มอีกนิด จึงร่ายเวทย์ต่อ * ทว่ากำไรเริ่มร่อยหรอ จนเหลือเพียงทุนเดิม สุดท้ายทุนที่ตั้งไว้คราแรกก็มลายสิ้น * จำต้องหาเงินทองมาลงเพิ่ม หวังทวงทุนคืน และพบว่าต้องสูญเสียเงินก้อนนั้นไปในห้วงเวลาต่อมา ลำดับเหตุการณ์ดังกล่าว เรียกได้ว่าเป็น “วงจรอุบาทว์” สำหรับนักพนันมากมายในเฮรันเทล ปริศนาที่ตามมาก็คือ เหตุใด “วงจรอุบาทว์” นี้จึงเกิดขึ้นซ้ำแล้วซ้ำเล่า? ส่วนหนึ่ง ย่อมเป็นเพราะอารมณ์อันแปรปรวนในการเสี่ยงโชคของแต่ละคน แต่อีกส่วนที่สำคัญยิ่งกว่า ต้องกล่าวว่าเป็นผลจาก “กลไกต้องสาป” ของจ้าวแห่งหอคอยรัตติกาล ซึ่งต้องกล่าวว่า เหล่าเจ้าของหอคอยรัตติกาลนั้น จักใช้หลักการทำนองเดียวกับ “สมาคมพ่อค้าผู้พิทักษ์” คือจักเก็บเงินทองจากชนจำนวนมาก เพื่อนำมาจ่ายให้กับชนเพียงหยิบมือ เพื่อล่อลวงให้ชนทั้งหลายเสี่ยงโชคต่อไป หรือทำให้เหล่านักพนันหวังว่า จักเป็นผู้โชคดีเฉกเช่นพวกเขาบ้าง แม้จะมีผู้โชคดีที่สามารถได้กำไรในเบื้องต้น แต่ในบั้นปลายก็จักพ่ายแพ้อยู่ดี ซึ่งเป็นไปตาม “กฎแห่งจำนวนมหาศาล” เพราะจ้าวแห่งหอคอยรัตติกาลนั้น ได้คำนวณและออกแบบระบบเกมที่ตนเองได้เปรียบในระยะยาวแล้ว จากตำนานนี้ ย่อมประจักษ์ชัดว่า แม้การพนันจักเป็นเรื่องของดวงชะตา แต่ก็ถูกรังสรรค์ขึ้นจากการคำนวณทางคณิตศาสตร์ ดังนั้น หากปรารถนาจะหาหนทางเอาชนะจ้าวแห่งหอคอยรัตติกาล ก็จำต้องเข้าใจ “คณิตศาสตร์” เสียก่อน ทีนี้ จงเงี่ยหูฟัง แล้วท่านจักได้ยินข้าไขปริศนา: ๑. ปริศนาแห่ง “กำไรคาดหวัง” สำหรับการแสวงหา “เกมเสี่ยงทาย” ที่ควรค่าแก่การเล่น หรือการเสี่ยง สิ่งแรกที่นักพนันพึงกระทำคือ “การประเมินกำไรคาดหวัง” หรือ “เวทคำนวณอนาคต” “กำไรคาดหวัง” ถูกคิดค้นโดย คริสเตียน ฮอยเกนส์ นักปราชญ์เวทย์ชาวดัตช์ เพื่อประเมินว่าเกมพนันแบบใดควรค่าแก่การเล่น ซึ่งมิใช่เพียงแค่การประเมินโอกาสแห่งชัยชนะเท่านั้น แต่ต้องคิดรวมขนาดของเงินเดิมพันไปด้วย โดยสูตรเวทย์คือ: กำไรคาดหวัง = (เงินที่ได้ x โอกาสชนะ) + (เงินที่เสีย x โอกาสแพ้) ดังนั้น หากปรารถนาจะสะสม “ทองคำมายา” ในระยะยาว จงเลือกเกมที่มี “กำไรคาดหวัง” เป็นบวก แต่หากพลาดพลั้งเข้าไปเล่นเกมที่ “กำไรคาดหวัง” เป็นลบ และบังเอิญว่าโชคชะตาเล่นตลกให้ได้เงินทองมาครอง พึงละทิ้งเกมนั้นเสียโดยพลัน เพราะท้ายที่สุดหากยังคงเล่นต่อไป ผู้อับโชคผู้นั้นก็คือตัวท่านเอง อย่างไรก็ตาม โดยธรรมดาแล้ว “กำไรคาดหวัง” ของเกมพนันที่มีเจ้ามือมักจักติดลบ จึงเป็นเรื่องยากยิ่งที่จะเอาชนะได้ เฉกเช่นตัวอย่างที่เราเห็น คือเกมในบ่อนพนัน หรือแม้แต่ “สลากกินแบ่งรัฐบาล” ก็ล้วนเป็นเกมที่มี “กำไรคาดหวัง” ติดลบทั้งสิ้น นอกจาก “กำไรคาดหวัง” จักถูกใช้กับการพนันได้แล้ว หลักเวทย์ “คณิตศาสตร์” ก็ยังสามารถประยุกต์ใช้กับการลงทุนได้ไม่แตกต่างกัน ตัวอย่างเช่น หากท่านเก็บสถิติข้อมูลการลงทุนของตนเอง แล้วพบว่ามีเพียงสามสิบส่วนร้อยเท่านั้น ที่ท่านซื้อ “ศิลาแห่งโชค” แล้วสร้างผลตอบแทนเป็นบวก แต่ท่านยังคงปรารถนาความสำเร็จในการลงทุน ก็จงจำกัดการขาดทุนแต่ละคราให้น้อยเข้าไว้ เช่น -๕% และปล่อยให้มีกำไรในแต่ละคราที่ลงทุน เช่น อย่างน้อย ๒๐% ซึ่งจากการใช้กลยุทธ์นี้ ท่านจักมี “กำไรคาดหวัง” = (๒๐% x ๐.๓) + (-๕% x ๐.๗) = ๒.๕% จักเห็นได้ว่า แม้ท่านจักมีจำนวนคราที่ขาดทุนบ่อยครั้ง แต่ก็ยังสามารถสร้างกำไรได้ หากคราที่กำไรนั้น สามารถทำเงินทองเป็นจำนวนมากได้ ๒. ปริศนาแห่ง “การบริหารหน้าตัก” หรือ “การบริหารเงินทุน” แม้ว่าท่านจักรับรู้ “กำไรคาดหวัง” แล้ว แต่หากท่านเผชิญหน้ากับการขาดทุนต่อเนื่องกัน ท่านก็อาจหมดเนื้อหมดตัวก่อนถึงคราที่จะกอบโกยเงินทองจากคราที่กำไร วิธีคลายปมปริศนานี้ก็คือ การมิลงเงินทองทั้งหมดของท่านในการลงทุนเพียงคราเดียว ซึ่งนอกจากการกระจายความเสี่ยงในการลงทุนหลาย “ศิลาแห่งโชค” หรือหลาย “เกมเสี่ยงทาย” แล้ว ท่านอาจกำหนดขนาดของการลงทุนแต่ละคราให้มิมากเกินไป แบบง่าย ๆ เช่น มิเกิน ๑๐% ของเงินลงทุนทั้งหมด หรือท่านอาจคำนวณขนาดของการลงทุนแต่ละคราด้วยสูตรทางคณิตศาสตร์ เช่น สูตร “การขาดทุนสูงสุดที่ท่านรับได้ (Value at Risk)” หรือ สูตร “ขนาดเดิมพันที่เหมาะสม (Kelly Formula)” ๓. ปริศนาแห่ง “อคติ” ในวงการพนัน มักมีอคติหนึ่งที่บังเกิดบ่อยครั้งกับผู้คน คือ “Gambler's Fallacy” หรือ “ความเชื่อผิด ๆ แห่งนักพนัน” ว่าหากเหตุการณ์หนึ่งบังเกิดบ่อยครั้งกว่าปรกติในช่วงเวลาหนึ่ง ๆ เหตุการณ์นั้นจักบังเกิดบ่อยครั้งน้อยลงในอนาคต ทั้ง ๆ ที่เหตุการณ์เหล่านั้นเป็นอิสระจากกันในทางสถิติ ยกตัวอย่างเช่น หากโยนเหรียญมนตราออกหัวไปแล้วสามครา ในคราที่สี่ หลายคนอาจคิดว่าโอกาสออกก้อยมากกว่าหัว แม้ว่าการโยนเหรียญแต่ละคราจะมิได้ส่งผลอันใดต่อกันเลย (จะโยนกี่ครา โอกาสหัวหรือก้อย ก็คือ ๕๐:๕๐ อยู่ยั่งยืน) หรือแม้กระทั่ง “สลากกินแบ่งรัฐบาล” มีหลายคนที่ซื้อเลขซ้ำกัน เพื่อหวังว่าจะถูกในงวดต่อ ๆ ไป ในวงการการลงทุน ก็มีลักษณะที่คล้ายคลึงกัน เช่น หาก “ศิลาแห่งโชค A” ราคาตกต่ำลงมาห้าครา บางคนอาจคิดว่าในคราที่หก ราคาของมันจักต้องเด้งขึ้นมา ซึ่งในความเป็นจริง หาได้เป็นเช่นนั้นเสมอไป จักเห็นได้ว่า แท้จริงแล้ว ไม่ว่าจักเป็น “เกมเสี่ยงทายแห่งโชคชะตา” หรือ “การผจญภัยในตลาดทุน” หากท่านมีความเข้าใจ และนำ “คณิตศาสตร์” เข้ามาเป็นรากฐาน มันก็อาจนำพาตัวท่านเอง ไปสู่จุดที่ได้เปรียบในเกมนั้น ได้เฉกเช่นกัน.. สูตรเวทย์มนตร์ที่ปรากฏในตำนาน: * กำไรคาดหวัง = (เงินที่ได้ x โอกาสชนะ) + (เงินที่เสีย x โอกาสแพ้) คำเตือนจากนักเล่าเรื่องแห่งเฮรันเทล: "พึงระลึกไว้เสมอว่า โชคชะตาเป็นสิ่งที่คาดเดาได้ยาก แม้เวทมนตร์คณิตศาสตร์จักช่วยนำทาง แต่ท้ายที่สุดแล้ว ความสำเร็จยังคงขึ้นอยู่กับการตัดสินใจและสติปัญญาของท่านเอง"
หวังว่าตำนานบทนี้จักเป็นประโยชน์แก่ท่านนะคะ
-
 @ 401014b3:59d5476b
2025-04-22 00:23:24
@ 401014b3:59d5476b
2025-04-22 00:23:24About Me
I come to Nostr with extensive experience in the digital landscape. As a blockchain native since 2017, I've witnessed the evolution of decentralized technologies firsthand. Most of my professional career has been spent working within big tech companies, giving me a unique perspective on both centralized and decentralized systems.
My social media journey began on Twitter in 2007, where I've maintained a presence for over 17 years. I've also explored other decentralized social platforms including BlueSky, Farcaster, and Lens Protocol. As a Bitcoin maximalist, I was particularly intrigued by Nostr's compatibility with the Lightning Network, which initially drew me to the platform.
The Onboarding Challenge
The Nostr onboarding experience presents a significant hurdle for newcomers. Despite my technical background in blockchain technologies, I found the initial setup process more complicated than expected. Understanding public/private key cryptography just to join a social network creates a steeper learning curve than necessary.
BlueSky and Farcaster have demonstrated that it's possible to maintain decentralized principles while providing a more streamlined onboarding experience. Their approaches show that user-friendly design and decentralization aren't mutually exclusive concepts.
Relay Management: Room for Improvement
The concept of relays represents one of Nostr's most distinctive features, though it can be confusing for newcomers. While many clients come pre-configured with default relays, users eventually encounter situations where content or connections seem inconsistent.
When someone I've interacted with doesn't appear in my feed or doesn't respond, I'm often left wondering if we're simply on different relays. This uncertainty creates friction that doesn't exist on other platforms where connectivity is handled behind the scenes.
The relay system introduces a layer of complexity that, while important to Nostr's architecture, could benefit from better abstraction in the user experience. When using BlueSky or Farcaster, I don't need to think about the underlying infrastructure, something Nostr could learn from while maintaining its decentralized principles.
The Zap Economy: Growing Pains
The Lightning-powered zap system shows tremendous potential, but I've observed some concerning economic patterns. Longer-term Nostr users have expressed frustration about continuously sending zaps while seeing limited growth in the overall ecosystem.
Interestingly, there appears to be a connection between this liquidity issue and community growth dynamics. Some established users who voice concerns about bearing the financial burden of the zapping economy are simultaneously less welcoming to newer accounts, rarely following, engaging with, or zapping newcomers.
This creates a challenging environment for new users, who face a cold reception and have little incentive to load their Lightning wallets or participate in the zap economy. Why bring fresh liquidity to a platform where established users rarely engage with your content? This dynamic has limited the expansion of the ecosystem, with the same sats often circulating among established users rather than growing with new participants.
Client Diversity: Strength and Challenge
Nostr's multiple client options offer users choice, which is valuable. However, the implementation of NIPs (Nostr Implementation Possibilities) varies across clients, creating inconsistent experiences. Features that work seamlessly in one client might be implemented differently in another.
This extends to fundamental aspects like search functionality, thread navigation, and notification systems, all of which can differ significantly between clients. For users accustomed to consistent experiences, this fragmentation creates a learning curve with each new client they try.
Lightning Integration: Varying Experiences
The Lightning Network integration varies in quality and user experience across Nostr clients. While the functionality is generally present, the implementation quality, feature set, and ease of use differ depending on which client you choose.
This inconsistency means users may need to experiment with several clients to find one that provides the Lightning experience they're looking for, rather than having a consistent experience across the ecosystem.
Finding Balance
Nostr appears to be navigating the challenge of balancing technical innovation with user experience. While its cryptographic foundation and decentralized architecture are impressive technical achievements, these same strengths sometimes come at the cost of accessibility.
Despite my technical background and interest in decentralized technologies, I find myself using BlueSky and Farcaster more frequently for daily social interactions, while checking Nostr less often. For Nostr to achieve its potential for broader adoption, addressing these user experience considerations while maintaining its core principles will be essential.
The platform has tremendous potential with improvements to user experience, community dynamics, and economic sustainability, Nostr could evolve from a fascinating technical experiment into a truly compelling alternative to mainstream social media.
-
 @ d360efec:14907b5f
2025-04-21 22:10:23
@ d360efec:14907b5f
2025-04-21 22:10:23สวัสดีเพื่อนนักเทรดทุกท่าน! 👋 วันนี้ฉันมาแนะนำตารางกิจวัตรประจำวันของ Day Trader ที่น่าสนใจนี้กันนะคะ มาดูกันว่ามีอะไรที่เราสามารถเรียนรู้และนำไปปรับใช้กับการเทรดของเราได้บ้างค่ะ

ภาพรวมกิจวัตรประจำวันของ Day Trader 📊
ตารางนี้แสดงให้เห็นถึงโครงสร้างของวันที่สมดุลสำหรับนักเทรดรายวันที่ประสบความสำเร็จ โดยเน้นทั้งการเตรียมตัว 🤓 การลงมือเทรด 🚀 การเรียนรู้ 📚 และการดูแลสุขภาพส่วนตัว 🧘♀️ ซึ่งเป็นสิ่งสำคัญอย่างยิ่งในการรักษาประสิทธิภาพและความสม่ำเสมอในการเทรด 💪
การวิเคราะห์และอธิบายแต่ละช่วงเวลา
$ 05.30 น. > ตื่นนอน 🌅 อาบน้ำ 🚿 และเตรียมตัว 👔 > การเริ่มต้นวันอย่างกระปรี้กระเปร่า 🎉 และการมีกิจวัตรส่วนตัวที่ผ่อนคลายเป็นสิ่งสำคัญในการเตรียมพร้อมทั้งร่างกายและจิตใจ 🧠 สำหรับการเทรด
$ 06.00 น. > ตรวจสอบข่าวสาร 📰 วิเคราะห์กราฟ 📈 และเตรียมตัว 🎯 > ช่วงเวลานี้เป็นหัวใจสำคัญของการเตรียมตัวก่อนตลาดเปิด ⏰ นักเทรดจะตรวจสอบข่าวเศรษฐกิจ 💰 และข่าวที่เกี่ยวข้องกับสินทรัพย์ที่ตนเองเทรด 🧐 วิเคราะห์กราฟเพื่อหาแนวโน้ม 🔭 และระดับราคาที่น่าสนใจ 📍 รวมถึงวางแผนกลยุทธ์การเทรดสำหรับวันนี้ ✍️
$ 06.30 น. > ตลาดเปิด 🔔 เริ่มทำการเทรด 🚀 > เมื่อตลาดเปิด นักเทรดจะเริ่มดำเนินการตามแผนที่วางไว้ 📝 โดยจะเฝ้าติดตามการเคลื่อนไหวของราคา 👀 และเข้าเทรดตามสัญญาณที่เกิดขึ้น 🚦
$ 12.00 น. > พักรับประทานอาหารกลางวัน 🥪 > การพักผ่อน 😌 และการเติมพลัง 💪 ในช่วงกลางวันเป็นสิ่งสำคัญในการรักษาความมีสมาธิ 🧘♀️ และความสามารถในการตัดสินใจที่ดี 👍
$ 12.45 น. > ปิดสถานะการเทรดทั้งหมด 🛑 > สำหรับ Day Trader การปิดสถานะทั้งหมดภายในวันถือเป็นกฎเหล็ก 🚫 เพื่อหลีกเลี่ยงความเสี่ยงจากความผันผวนข้ามคืน 🌙
$ 13.00 น. > ทบทวน 🤔 เรียนรู้ 📚 และปรับปรุง ⚙️ > หลังจากการเทรด นักเทรดที่ประสบความสำเร็จ 🎉 จะใช้เวลาในการทบทวนการเทรดของตนเอง 🧐 วิเคราะห์ว่าอะไรทำได้ดี 👍 และอะไรที่ต้องปรับปรุง 📝 การเรียนรู้อย่างต่อเนื่องเป็นกุญแจสำคัญสู่การพัฒนา 🚀
$ 14.00 น. > ออกกำลังกาย 💪 และพักผ่อน 🧘♀️ > การดูแลสุขภาพกาย 🍎 และใจ 💖 มีความสำคัญไม่ยิ่งหย่อนไปกว่าการเทรด 📈 การออกกำลังกายและการมีเวลาว่าง 🌴 ช่วยลดความเครียด 😥 และเพิ่มประสิทธิภาพในการเทรดในระยะยาว ✨
$ 17.00 น. > รับประทานอาหารเย็น 🍽️ และพักผ่อน 🛋️ > การมีเวลาพักผ่อนกับครอบครัว ❤️ หรือทำกิจกรรมที่ชอบ 😊 ช่วยให้ผ่อนคลาย 😌 และเตรียมพร้อมสำหรับวันต่อไป 🌅
$ 19.00 น. > วางแผนการเทรดสำหรับวันพรุ่งนี้ 🗓️ และตรวจสอบข่าวสาร 📰 > การวางแผนล่วงหน้า 🤓 ช่วยให้นักเทรดมีความพร้อม 💪 และสามารถตอบสนองต่อสถานการณ์ตลาดได้อย่างมีประสิทธิภาพ 🚀
$ 22.00 น. > เข้านอน 😴 > การนอนหลับพักผ่อนอย่างเพียงพอ 🛌 เป็นสิ่งจำเป็นสำหรับการรักษาสุขภาพ 💖 และประสิทธิภาพในการเทรด 💪
สิ่งที่น่าสนใจและข้อคิด 🤔
$ ความมีระเบียบวินัย 💯 > ตารางนี้แสดงให้เห็นถึงความมีระเบียบวินัยที่เข้มงวด 📏 ซึ่งเป็นคุณสมบัติที่สำคัญของนักเทรดที่ประสบความสำเร็จ 🎉
$ การเตรียมตัวอย่างรอบคอบ 🧐 > การใช้เวลาในการวิเคราะห์ 📊 และวางแผน 📝 ก่อนตลาดเปิดช่วยลดการตัดสินใจที่ผิดพลาด 🚫 และเพิ่มโอกาสในการทำกำไร 💰
$ การเรียนรู้อย่างต่อเนื่อง 📚 > การทบทวน 🤔 และปรับปรุงกลยุทธ์ ⚙️ อยู่เสมอเป็นสิ่งสำคัญในการพัฒนาทักษะการเทรด 🚀
$ ความสมดุล ⚖️ > การให้ความสำคัญกับการดูแลสุขภาพ 🧘♀️ และการพักผ่อน 🌴 ควบคู่ไปกับการเทรด 📈 ช่วยป้องกันภาวะหมดไฟ 🔥 และรักษาประสิทธิภาพในระยะยาว ✨
การนำไปปรับใช้ 🛠️
เพื่อนๆ นักเทรดสามารถนำแนวคิดจากตารางนี้ไปปรับใช้กับกิจวัตรประจำวันของตนเองได้ 👍 โดยอาจไม่จำเป็นต้องทำตามทุกช่วงเวลาอย่างเคร่งครัด ⏰ แต่ให้เน้นที่หลักการสำคัญ เช่น การเตรียมตัวก่อนเทรด 🤓 การทบทวนหลังเทรด 🤔 และการดูแลสุขภาพ 🧘♀️ เพื่อสร้างสมดุล ⚖️ และเพิ่มประสิทธิภาพในการเทรดของเราค่ะ 💪
ขอให้ทุกท่านประสบความสำเร็จในการเทรดนะคะ! 💸🚀
#DayTrader #นักเทรดรายวัน #กิจวัตรประจำวัน #การลงทุน #เทรด #หุ้น #คริปโต #ตลาดหุ้น #แรงบันดาลใจ #พัฒนาตัวเอง #LinaEngword
-
 @ 4ba8e86d:89d32de4
2025-04-21 02:12:19
@ 4ba8e86d:89d32de4
2025-04-21 02:12:19SISTEMA OPERACIONAL MÓVEIS
GrapheneOS : https://njump.me/nevent1qqs8t76evdgrg4qegdtyrq2rved63pr29wlqyj627n9tj4vlu66tqpqpzdmhxue69uhk7enxvd5xz6tw9ec82c30qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqppcqec9
CalyxOS : https://njump.me/nevent1qqsrm0lws2atln2kt3cqjacathnw0uj0jsxwklt37p7t380hl8mmstcpydmhxue69uhkummnw3ez6an9wf5kv6t9vsh8wetvd3hhyer9wghxuet59uq3vamnwvaz7tmwdaehgu3wvf3kstnwd9hx5cf0qy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgcwaehxw309aex2mrp0yhxxatjwfjkuapwveukjtcpzpmhxue69uhkummnw3ezumt0d5hszrnhwden5te0dehhxtnvdakz7qfywaehxw309ahx7um5wgh8ymm4dej8ymmrdd3xjarrda5kuetjwvhxxmmd9uq3uamnwvaz7tmwdaehgu3dv3jhvtnhv4kxcmmjv3jhytnwv46z7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qgewaehxw309ahx7um5wghxymmwva3x7mn89e3k7mf0qythwumn8ghj7cn5vvhxkmr9dejxz7n49e3k7mf0qyg8wumn8ghj7mn09eehgu3wvdez7smttdu
LineageOS : https://njump.me/nevent1qqsgw7sr36gaty48cf4snw0ezg5mg4atzhqayuge752esd469p26qfgpzdmhxue69uhhwmm59e6hg7r09ehkuef0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpnvm779
SISTEMA OPERACIONAL DESKTOP
Tails : https://njump.me/nevent1qqsf09ztvuu60g6xprazv2vxqqy5qlxjs4dkc9d36ta48q75cs9le4qpzemhxue69uhkummnw3ex2mrfw3jhxtn0wfnj7q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz34ag5t
Qubes OS : https://njump.me/nevent1qqsp6jujgwl68uvurw0cw3hfhr40xq20sj7rl3z4yzwnhp9sdpa7augpzpmhxue69uhkummnw3ezumt0d5hsz9mhwden5te0wfjkccte9ehx7um5wghxyctwvshsz9thwden5te0dehhxarj9ehhsarj9ejx2a30qyg8wumn8ghj7mn09eehgu3wvdez7qg4waehxw309aex2mrp0yhxgctdw4eju6t09uqjxamnwvaz7tmwdaehgu3dwejhy6txd9jkgtnhv4kxcmmjv3jhytnwv46z7qgwwaehxw309ahx7uewd3hkctcpremhxue69uhkummnw3ez6er9wch8wetvd3hhyer9wghxuet59uj3ljr8
Kali linux : https://njump.me/nevent1qqswlav72xdvamuyp9xc38c6t7070l3n2uxu67ssmal2g7gv35nmvhspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqswt9rxe
Whonix : https://njump.me/nevent1qqs85gvejvzhk086lwh6edma7fv07p5c3wnwnxnzthwwntg2x6773egpydmhxue69uhkummnw3ez6an9wf5kv6t9vsh8wetvd3hhyer9wghxuet59uq3qamnwvaz7tmwdaehgu3wd4hk6tcpzemhxue69uhkummnw3ezucnrdqhxu6twdfsj7qfywaehxw309ahx7um5wgh8ymm4dej8ymmrdd3xjarrda5kuetjwvhxxmmd9uq3wamnwvaz7tmzw33ju6mvv4hxgct6w5hxxmmd9uq3qamnwvaz7tmwduh8xarj9e3hytcpzamhxue69uhhyetvv9ujumn0wd68ytnzv9hxgtcpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhszrnhwden5te0dehhxtnvdakz7qg7waehxw309ahx7um5wgkkgetk9emk2mrvdaexgetj9ehx2ap0sen9p6
Kodachi : https://njump.me/nevent1qqsf5zszgurpd0vwdznzk98hck294zygw0s8dah6fpd309ecpreqtrgpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhszgmhwden5te0dehhxarj94mx2unfve5k2epwwajkcmr0wfjx2u3wdejhgtcpremhxue69uhkummnw3ez6er9wch8wetvd3hhyer9wghxuet59uq3qamnwvaz7tmwdaehgu3wd4hk6tcpzamhxue69uhkyarr9e4kcetwv3sh5afwvdhk6tcpzpmhxue69uhkumewwd68ytnrwghszfrhwden5te0dehhxarj9eex7atwv3ex7cmtvf5hgcm0d9hx2unn9e3k7mf0qyvhwumn8ghj7mn0wd68ytnzdahxwcn0denjucm0d5hszrnhwden5te0dehhxtnvdakz7qgkwaehxw309ahx7um5wghxycmg9ehxjmn2vyhsz9mhwden5te0wfjkccte9ehx7um5wghxyctwvshs94a4d5
PGP
Openkeychain : https://njump.me/nevent1qqs9qtjgsulp76t7jkquf8nk8txs2ftsr0qke6mjmsc2svtwfvswzyqpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs36mp0w
Kleopatra : https://njump.me/nevent1qqspnevn932hdggvp4zam6mfyce0hmnxsp9wp8htpumq9vm3anq6etsppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpuaeghp
Pgp : https://njump.me/nevent1qqsggek707qf3rzttextmgqhym6d4g479jdnlnj78j96y0ut0x9nemcpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgptemhe
Como funciona o PGP? : https://njump.me/nevent1qqsz9r7azc8pkvfmkg2hv0nufaexjtnvga0yl85x9hu7ptpg20gxxpspremhxue69uhkummnw3ez6ur4vgh8wetvd3hhyer9wghxuet59upzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqy259fhs
Por que eu escrevi PGP. - Philip Zimmermann.
https://njump.me/nevent1qqsvysn94gm8prxn3jw04r0xwc6sngkskg756z48jsyrmqssvxtm7ncpzamhxue69uhhyetvv9ujumn0wd68ytnzv9hxgtchzxnad
VPN
Vpn : https://njump.me/nevent1qqs27ltgsr6mh4ffpseexz6s37355df3zsur709d0s89u2nugpcygsspzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqshzu2fk
InviZible Pro : https://njump.me/nevent1qqsvyevf2vld23a3xrpvarc72ndpcmfvc3lc45jej0j5kcsg36jq53cpz3mhxue69uhhyetvv9ujuerpd46hxtnfdupzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqy33y5l4
Orbot: https://njump.me/nevent1qqsxswkyt6pe34egxp9w70cy83h40ururj6m9sxjdmfass4cjm4495stft593
I2P
i2p : https://njump.me/nevent1qqsvnj8n983r4knwjmnkfyum242q4c0cnd338l4z8p0m6xsmx89mxkslx0pgg
Entendendo e usando a rede I2P : https://njump.me/nevent1qqsxchp5ycpatjf5s4ag25jkawmw6kkf64vl43vnprxdcwrpnms9qkcppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpvht4mn
Criando e acessando sua conta Email na I2P : https://njump.me/nevent1qqs9v9dz897kh8e5lfar0dl7ljltf2fpdathsn3dkdsq7wg4ksr8xfgpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpw8mzum
APLICATIVO 2FA
Aegis Authenticator : https://njump.me/nevent1qqsfttdwcn9equlrmtf9n6wee7lqntppzm03pzdcj4cdnxel3pz44zspz4mhxue69uhhyetvv9ujumn0wd68ytnzvuhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqscvtydq
YubiKey : https://njump.me/nevent1qqstsnn69y4sf4330n7039zxm7wza3ch7sn6plhzmd57w6j9jssavtspvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzueyvgt
GERENCIADOR DE SENHAS
KeepassDX: https://njump.me/nevent1qqswc850dr4ujvxnmpx75jauflf4arc93pqsty5pv8hxdm7lcw8ee8qpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpe0492n
Birwaden: https://njump.me/nevent1qqs0j5x9guk2v6xumhwqmftmcz736m9nm9wzacqwjarxmh8k4xdyzwgpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpwfe2kc
KeePassXC: https://njump.me/nevent1qqsgftcrd8eau7tzr2p9lecuaf7z8mx5jl9w2k66ae3lzkw5wqcy5pcl2achp
CHAT MENSAGEM
SimpleXchat : https://njump.me/nevent1qqsds5xselnnu0dyy0j49peuun72snxcgn3u55d2320n37rja9gk8lgzyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgmcmj7c
Briar : https://njump.me/nevent1qqs8rrtgvjr499hreugetrl7adkhsj2zextyfsukq5aa7wxthrgcqcg05n434
Element Messenger : https://njump.me/nevent1qqsq05snlqtxm5cpzkshlf8n5d5rj9383vjytkvqp5gta37hpuwt4mqyccee6
Pidgin : https://njump.me/nevent1qqsz7kngycyx7meckx53xk8ahk98jkh400usrvykh480xa4ct9zlx2c2ywvx3
E-MAIL
Thunderbird: https://njump.me/nevent1qqspq64gg0nw7t60zsvea5eykgrm43paz845e4jn74muw5qzdvve7uqrkwtjh
ProtonMail : https://njump.me/nevent1qqs908glhk68e7ms8zqtlsqd00wu3prnpt08dwre26hd6e5fhqdw99cppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpeyhg4z
Tutonota : https://njump.me/nevent1qqswtzh9zjxfey644qy4jsdh9465qcqd2wefx0jxa54gdckxjvkrrmqpz4mhxue69uhhyetvv9ujumt0wd68ytnsw43qygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs5hzhkv
k-9 mail : https://njump.me/nevent1qqs200g5a603y7utjgjk320r3srurrc4r66nv93mcg0x9umrw52ku5gpr3mhxue69uhkummnw3ezuumhd9ehxtt9de5kwmtp9e3kstczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgacflak
E-MAIL-ALIÁS
Simplelogin : https://njump.me/nevent1qqsvhz5pxqpqzr2ptanqyqgsjr50v7u9lc083fvdnglhrv36rnceppcppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqp9gsr7m
AnonAddy : https://njump.me/nevent1qqs9mcth70mkq2z25ws634qfn7vx2mlva3tkllayxergw0s7p8d3ggcpzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs6mawe3
NAVEGADOR
Navegador Tor : https://njump.me/nevent1qqs06qfxy7wzqmk76l5d8vwyg6mvcye864xla5up52fy5sptcdy39lspzemhxue69uhkummnw3ezuerpw3sju6rpw4ej7q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzdp0urw
Mullvap Browser : https://njump.me/nevent1qqs2vsgc3wk09wdspv2mezltgg7nfdg97g0a0m5cmvkvr4nrfxluzfcpzdmhxue69uhhwmm59e6hg7r09ehkuef0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpj8h6fe
LibreWolf : https://njump.me/nevent1qqswv05mlmkcuvwhe8x3u5f0kgwzug7n2ltm68fr3j06xy9qalxwq2cpzemhxue69uhkummnw3ex2mrfw3jhxtn0wfnj7q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzuv2hxr
Cromite : https://njump.me/nevent1qqs2ut83arlu735xp8jf87w5m3vykl4lv5nwkhldkqwu3l86khzzy4cpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs3dplt7
BUSCADORES
Searx : https://njump.me/nevent1qqsxyzpvgzx00n50nrlgctmy497vkm2cm8dd5pdp7fmw6uh8xnxdmaspr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqp23z7ax
APP-STORE
Obtainium : https://njump.me/nevent1qqstd8kzc5w3t2v6dgf36z0qrruufzfgnc53rj88zcjgsagj5c5k4rgpz3mhxue69uhhyetvv9ujuerpd46hxtnfdupzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqyarmca3
F-Droid : https://njump.me/nevent1qqst4kry49cc9g3g8s5gdnpgyk3gjte079jdnv43f0x4e85cjkxzjesymzuu4
Droid-ify : https://njump.me/nevent1qqsrr8yu9luq0gud902erdh8gw2lfunpe93uc2u6g8rh9ep7wt3v4sgpzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsfzu9vk
Aurora Store : https://njump.me/nevent1qqsy69kcaf0zkcg0qnu90mtk46ly3p2jplgpzgk62wzspjqjft4fpjgpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzrpmsjy
RSS
Feeder : https://njump.me/nevent1qqsy29aeggpkmrc7t3c7y7ldgda7pszl7c8hh9zux80gjzrfvlhfhwqpp4mhxue69uhkummn9ekx7mqzyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgsvzzjy
VIDEOO CONFERENCIA
Jitsi meet : https://njump.me/nevent1qqswphw67hr6qmt2fpugcj77jrk7qkfdrszum7vw7n2cu6cx4r6sh4cgkderr
TECLADOS
HeliBoard : https://njump.me/nevent1qqsyqpc4d28rje03dcvshv4xserftahhpeylu2ez2jutdxwds4e8syspz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsr8mel5
OpenBoard : https://njump.me/nevent1qqsf7zqkup03yysy67y43nj48q53sr6yym38es655fh9fp6nxpl7rqspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqswcvh3r
FlorisBoard : https://njump.me/nevent1qqsf7zqkup03yysy67y43nj48q53sr6yym38es655fh9fp6nxpl7rqspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqswcvh3r
MAPAS
Osmand : https://njump.me/nevent1qqsxryp2ywj64az7n5p6jq5tn3tx5jv05te48dtmmt3lf94ydtgy4fgpzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs54nwpj
Organic maps : https://njump.me/nevent1qqstrecuuzkw0dyusxdq7cuwju0ftskl7anx978s5dyn4pnldrkckzqpr4mhxue69uhkummnw3ezumtp0p5k6ctrd96xzer9dshx7un8qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpl8z3kk
TRADUÇÃO
LibreTranslate : https://njump.me/nevent1qqs953g3rhf0m8jh59204uskzz56em9xdrjkelv4wnkr07huk20442cpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzeqsx40
REMOÇÃO DOS METADADOS
Scrambled Exif : https://njump.me/nevent1qqs2658t702xv66p000y4mlhnvadmdxwzzfzcjkjf7kedrclr3ej7aspyfmhxue69uhk6atvw35hqmr90pjhytngw4eh5mmwv4nhjtnhdaexcep0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpguu0wh
ESTEGANOGRAFIA
PixelKnot: https://njump.me/nevent1qqsrh0yh9mg0lx86t5wcmhh97wm6n4v0radh6sd0554ugn354wqdj8gpz3mhxue69uhhyetvv9ujuerpd46hxtnfdupzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqyuvfqdp
PERFIL DE TRABALHO
Shelter : https://njump.me/nevent1qqspv9xxkmfp40cxgjuyfsyczndzmpnl83e7gugm7480mp9zhv50wkqpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzdnu59c
PDF
MuPDF : https://njump.me/nevent1qqspn5lhe0dteys6npsrntmv2g470st8kh8p7hxxgmymqa95ejvxvfcpzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs4hvhvj
Librera Reader : https://njump.me/nevent1qqsg60flpuf00sash48fexvwxkly2j5z9wjvjrzt883t3eqng293f3cpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz39tt3n
QR-Code
Binary Eye : https://njump.me/nevent1qqsz4n0uxxx3q5m0r42n9key3hchtwyp73hgh8l958rtmae5u2khgpgpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzdmn4wp
Climático
Breezy Weather : https://njump.me/nevent1qqs9hjz5cz0y4am3kj33xn536uq85ydva775eqrml52mtnnpe898rzspzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgpd3tu8
ENCRYPTS
Cryptomator : https://njump.me/nevent1qqsvchvnw779m20583llgg5nlu6ph5psewetlczfac5vgw83ydmfndspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsx7ppw9
VeraCrypt : https://njump.me/nevent1qqsf6wzedsnrgq6hjk5c4jj66dxnplqwc4ygr46l8z3gfh38q2fdlwgm65ej3
EXTENSÕES
uBlock Origin : https://njump.me/nevent1qqswaa666lcj2c4nhnea8u4agjtu4l8q89xjln0yrngj7ssh72ntwzql8ssdj
Snowflake : https://njump.me/nevent1qqs0ws74zlt8uced3p2vee9td8x7vln2mkacp8szdufvs2ed94ctnwchce008
CLOUD
Nextcloud : https://njump.me/nevent1qqs2utg5z9htegdtrnllreuhypkk2026x8a0xdsmfczg9wdl8rgrcgg9nhgnm
NOTEPAD
Joplin : https://njump.me/nevent1qqsz2a0laecpelsznser3xd0jfa6ch2vpxtkx6vm6qg24e78xttpk0cpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpdu0hft
Standard Notes : https://njump.me/nevent1qqsv3596kz3qung5v23cjc4cpq7rqxg08y36rmzgcrvw5whtme83y3s7tng6r
MÚSICA
RiMusic : https://njump.me/nevent1qqsv3genqav2tfjllp86ust4umxm8tr2wd9kq8x7vrjq6ssp363mn0gpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqg42353n
ViMusic : https://njump.me/nevent1qqswx78559l4jsxsrygd8kj32sch4qu57stxq0z6twwl450vp39pdqqpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzjg863j
PODCAST
AntennaPod : https://njump.me/nevent1qqsp4nh7k4a6zymfwqqdlxuz8ua6kdhvgeeh3uxf2c9rtp9u3e9ku8qnr8lmy
VISUALIZAR VIDEO
VLC : https://njump.me/nevent1qqs0lz56wtlr2eye4ajs2gzn2r0dscw4y66wezhx0mue6dffth8zugcl9laky
YOUTUBE
NewPipe : https://njump.me/nevent1qqsdg06qpcjdnlvgm4xzqdap0dgjrkjewhmh4j3v4mxdl4rjh8768mgdw9uln
FreeTube : https://njump.me/nevent1qqsz6y6z7ze5gs56s8seaws8v6m6j2zu0pxa955dhq3ythmexak38mcpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs5lkjvv
LibreTube : https://snort.social/e/nevent1qqstmd5m6wrdvn4gxf8xyhrwnlyaxmr89c9kjddvnvux6603f84t3fqpz4mhxue69uhhyetvv9ujumt0wd68ytnsw43qygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsswwznc
COMPARTILHAMENTO DE ARQUIVOS
OnionShare : https://njump.me/nevent1qqsr0a4ml5nu6ud5k9yzyawcd9arznnwkrc27dzzc95q6r50xmdff6qpydmhxue69uhkummnw3ez6an9wf5kv6t9vsh8wetvd3hhyer9wghxuet59uq3uamnwvaz7tmwdaehgu3dv3jhvtnhv4kxcmmjv3jhytnwv46z7qgswaehxw309ahx7tnnw3ezucmj9uq32amnwvaz7tmjv4kxz7fwv3sk6atn9e5k7tcpzamhxue69uhkyarr9e4kcetwv3sh5afwvdhk6tcpzemhxue69uhkummnw3ezucnrdqhxu6twdfsj7qgswaehxw309ahx7um5wghx6mmd9uqjgamnwvaz7tmwdaehgu3wwfhh2mnywfhkx6mzd96xxmmfdejhyuewvdhk6tcppemhxue69uhkummn9ekx7mp0qythwumn8ghj7un9d3shjtnwdaehgu3wvfskuep0qyv8wumn8ghj7un9d3shjtnrw4e8yetwwshxv7tf9ut7qurt
Localsend : https://njump.me/nevent1qqsp8ldjhrxm09cvvcak20hrc0g8qju9f67pw7rxr2y3euyggw9284gpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzuyghqr
Wallet Bitcoin
Ashigaru Wallet : https://njump.me/nevent1qqstx9fz8kf24wgl26un8usxwsqjvuec9f8q392llmga75tw0kfarfcpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgvfsrqp
Samourai Wallet : https://njump.me/nevent1qqstcvjmz39rmrnrv7t5cl6p3x7pzj6jsspyh4s4vcwd2lugmre04ecpr9mhxue69uhkummnw3ezucn0denkymmwvuhxxmmd9upzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqy3rg4qs
CÂMERA
opencamera : https://njump.me/nevent1qqs25glp6dh0crrjutxrgdjlnx9gtqpjtrkg29hlf7382aeyjd77jlqpzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqssxcvgc
OFFICE
Collabora Office : https://njump.me/nevent1qqs8yn4ys6adpmeu3edmf580jhc3wluvlf823cc4ft4h0uqmfzdf99qpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsj40uss
TEXTOS
O manifesto de um Cypherpunk : https://njump.me/nevent1qqsd7hdlg6galn5mcuv3pm3ryfjxc4tkyph0cfqqe4du4dr4z8amqyspvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzal0efa
Operations security ( OPSEC) : https://snort.social/e/nevent1qqsp323havh3y9nxzd4qmm60hw87tm9gjns0mtzg8y309uf9mv85cqcpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz8ej9l7
O MANIFESTO CRIPTOANARQUISTA Timothy C. May – 1992. : https://njump.me/nevent1qqspp480wtyx2zhtwpu5gptrl8duv9rvq3mug85mp4d54qzywk3zq9gpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz5wq496
Declaração de independência do ciberespaço
- John Perry Barlow - 1996 : https://njump.me/nevent1qqs2njsy44n6p07mhgt2tnragvchasv386nf20ua5wklxqpttf6mzuqpzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsukg4hr
The Cyphernomicon: Criptografia, Dinheiro Digital e o Futuro da Privacidade. escrito por Timothy C. May -Publicado em 1994. :
Livro completo em PDF no Github PrivacyOpenSource.
https://github.com/Alexemidio/PrivacyOpenSource/raw/main/Livros/THE%20CYPHERNOMICON%20.pdf Share
-
 @ 65f03c16:f77e9d92
2025-04-20 08:33:37
@ 65f03c16:f77e9d92
2025-04-20 08:33:37is a game changer for traders. It blends chaos theory & market psychology to decode price action. Learn to spot order in market noise using fractals & momentum, teaches the Alligator indicator to ride trends & avoid chop. His 5-stage approach, from novice to expert, builds discipline & edge. Perfect for futures or stocks, It’s practical, not abstract. Williams’ 40+ yrs of trading shine through, with tools like Elliott Wave & nonlinear dynamics
recommended !
-
 @ 9223d2fa:b57e3de7
2025-04-15 15:35:00
@ 9223d2fa:b57e3de7
2025-04-15 15:35:004,220 steps
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ f839fb67:5c930939
2025-04-13 19:48:48
@ f839fb67:5c930939
2025-04-13 19:48:48Relays
| Name | Address | Price (Sats/Year) | Status | | - | - | - | - | | stephen's aegis relay | wss://paid.relay.vanderwarker.family | 42069 |
| | stephen's Outbox | wss://relay.vanderwarker.family | Just Me |
| | stephen's Inbox | wss://haven.vanderwarker.family/inbox | WoT |
| | stephen's DMs | wss://haven.vanderwarker.family/chat | WoT |
| | VFam Data Relay | wss://data.relay.vanderwarker.family | 0 |
| | VFam Bots Relay | wss://skeme.vanderwarker.family | Invite |
| | VFGroups (NIP29) | wss://groups.vanderwarker.family | 0 |
| | [TOR] My Phone Relay | ws://naswsosuewqxyf7ov7gr7igc4tq2rbtqoxxirwyhkbuns4lwc3iowwid.onion | 0 | Meh... |
My Pubkeys
| Name | hex | nprofile | | - | - | - | | Main | f839fb6714598a7233d09dbd42af82cc9781d0faa57474f1841af90b5c930939 | nostr:nprofile1qqs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3us9mapfx | | Vanity (Backup) | 82f21be67353c0d68438003fe6e56a35e2a57c49e0899b368b5ca7aa8dde7c23 | nostr:nprofile1qqsg9usmuee48sxkssuqq0lxu44rtc4903y7pzvmx694efa23h08cgcpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3ussel49x | | VFStore | 6416f1e658ba00d42107b05ad9bf485c7e46698217e0c19f0dc2e125de3af0d0 | nostr:nprofile1qqsxg9h3uevt5qx5yyrmqkkehay9cljxdxpp0cxpnuxu9cf9mca0p5qpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3usaa8plu | | NostrSMS | 9be1b8315248eeb20f9d9ab2717d1750e4f27489eab1fa531d679dadd34c2f8d | nostr:nprofile1qqsfhcdcx9fy3m4jp7we4vn305t4pe8jwjy74v062vwk08dd6dxzlrgpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3us595d45 |
Bots
Unlocks Bot
Hex: 2e941ad17144e0a04d1b8c21c4a0dbc3fbcbb9d08ae622b5f9c85341fac7c2d0
nprofile:
nostr:nprofile1qqsza9q669c5fc9qf5dccgwy5rdu877th8gg4e3zkhuus56pltru95qpramhxue69uhhx6m9d4jjuanpdejx2unhv9exketj9enxzmtfd3ust4kvak
Latest Data:
nostr:naddr1qq882mnvda3kkttrda6kuar9wgq37amnwvaz7tmnddjk6efwweskuer9wfmkzuntv4ezuenpd45kc7gzyqhfgxk3w9zwpgzdrwxzr39qm0plhjae6z9wvg44l8y9xs06clpdqqcyqqq823cgnl9u5Step Counter
Hex: 9223d2faeb95853b4d224a184c69e1df16648d35067a88cdf947c631b57e3de7
nprofile: nostr:nprofile1qqsfyg7jlt4etpfmf53y5xzvd8sa79ny356sv75gehu50333k4lrmecpramhxue69uhhx6m9d4jjuanpdejx2unhv9exketj9enxzmtfd3ustswp3w
Latest Data:
nostr:naddr1qvzqqqr4gupzpy3r6tawh9v98dxjyjscf357rhckvjxn2pn63rxlj37xxx6hu008qys8wumn8ghj7umtv4kk2tnkv9hxgetjwashy6m9wghxvctdd9k8jtcqp3ehgets943k7atww3jhyn39gffRCTGuest
Hex: 373904615c781e46bf5bf87b4126c8a568a05393b1b840b1a2a3234d20affa0c
nprofile: nostr:nprofile1qqsrwwgyv9w8s8jxhadls76pymy2269q2wfmrwzqkx32xg6dyzhl5rqpramhxue69uhhx6m9d4jjuanpdejx2unhv9exketj9enxzmtfd3usy92jlx
NIP-29 Groups
- Minecraft Group Chat
nostr:naddr1qqrxvc33xpnxxqfqwaehxw309anhymm4wpejuanpdejx2unhv9exketj9enxzmtfd3usygrzymrpd2wz8ularp06y8ad5dgaddlumyt7tfzqge3vc97sgsarjvpsgqqqnpvqazypfd- VFNet Group Chat
nostr:naddr1qqrrwvfjx9jxzqfqwaehxw309anhymm4wpejuanpdejx2unhv9exketj9enxzmtfd3usygrzymrpd2wz8ularp06y8ad5dgaddlumyt7tfzqge3vc97sgsarjvpsgqqqnpvq08hx48
"Nostrified Websites"
[D] = Saves darkmode preferences over nostr
[A] = Auth over nostr
[B] = Beta (software)
[z] = zap enabled
Other Services (Hosted code)
Emojis Packs
- Minecraft
nostr:naddr1qqy566twv43hyctxwsq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82nsd0k5wp- AIM
nostr:naddr1qqxxz6tdv4kk7arfvdhkuucpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3usyg8c88akw9ze3fer85yah4p2lqkvj7qap749w360rpq6ly94eycf8ypsgqqqw48qe0j2yk- Blobs
nostr:naddr1qqz5ymr0vfesz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqa2wek4ukj- FavEmojis
nostr:naddr1qqy5vctkg4kk76nfwvq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82nsf7sdwt- Modern Family
nostr:naddr1qqx56mmyv4exugzxv9kkjmreqy0hwumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jq3qlqulkec5tx98yv7snk759tuzejtcr5865468fuvyrtuskhynpyusxpqqqp65ujlj36n- nostriches (Amethyst collection)
nostr:naddr1qq9xummnw3exjcmgv4esz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqa2w2sqg6w- Pepe
nostr:naddr1qqz9qetsv5q37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82ns85f6x7- Minecraft Font
nostr:naddr1qq8y66twv43hyctxwssyvmmwwsq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82nsmzftgr- Archer Font
nostr:naddr1qq95zunrdpjhygzxdah8gqglwaehxw309aex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0ypzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqvzqqqr4fclkyxsh- SMB Font
nostr:naddr1qqv4xatsv4ezqntpwf5k7gzzwfhhg6r9wfejq3n0de6qz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqa2w0wqpuk
Git Over Nostr
- NostrSMS
nostr:naddr1qqyxummnw3e8xmtnqy0hwumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jqfrwaehxw309amk7apwwfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqyj8wumn8ghj7urpd9jzuun9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jqg5waehxw309aex2mrp0yhxgctdw4eju6t0qyxhwumn8ghj7mn0wvhxcmmvqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqaueqp0epk- nip51backup
nostr:naddr1qq9ku6tsx5ckyctrdd6hqqglwaehxw309aex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0yqjxamnwvaz7tmhda6zuun9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jqfywaehxw309acxz6ty9eex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0yq3gamnwvaz7tmjv4kxz7fwv3sk6atn9e5k7qgdwaehxw309ahx7uewd3hkcq3qlqulkec5tx98yv7snk759tuzejtcr5865468fuvyrtuskhynpyusxpqqqpmej4gtqs6- bukkitstr
nostr:naddr1qqykyattdd5hgum5wgq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gpydmhxue69uhhwmm59eex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0yqjgamnwvaz7tmsv95kgtnjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gpz3mhxue69uhhyetvv9ujuerpd46hxtnfduqs6amnwvaz7tmwdaejumr0dspzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqvzqqqrhnyf6g0n2
Market Places
Please use Nostr Market or somthing simular, to view.
- VFStore
nostr:naddr1qqjx2v34xe3kxvpn95cnqven956rwvpc95unscn9943kxet98q6nxde58p3ryqglwaehxw309aex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0yqjvamnwvaz7tmgv9mx2m3wweskuer9wfmkzuntv4ezuenpd45kc7f0da6hgcn00qqjgamnwvaz7tmsv95kgtnjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gpydmhxue69uhhwmm59eex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0ypzqeqk78n93wsq6sss0vz6mxl5shr7ge5cy9lqcx0smshpyh0r4uxsqvzqqqr4gvlfm7gu
Badges
Created
- paidrelayvf
nostr:naddr1qq9hqctfv3ex2mrp09mxvqglwaehxw309aex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0ypzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqvzqqqr48y85v3u3- iPow
nostr:naddr1qqzxj5r02uq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82wgg02u0r- codmaster
nostr:naddr1qqykxmmyd4shxar9wgq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82wgk3gm4g- iMine
nostr:naddr1qqzkjntfdejsz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqafed5s4x5
Clients I Use
- Amethyst
nostr:naddr1qqxnzd3cx5urqv3nxymngdphqgsyvrp9u6p0mfur9dfdru3d853tx9mdjuhkphxuxgfwmryja7zsvhqrqsqqql8kavfpw3- noStrudel
nostr:naddr1qqxnzd3cxccrvd34xser2dpkqy28wumn8ghj7un9d3shjtnyv9kh2uewd9hsygpxdq27pjfppharynrvhg6h8v2taeya5ssf49zkl9yyu5gxe4qg55psgqqq0nmq5mza9n- nostrsms
nostr:naddr1qq9rzdejxcunxde4xymqz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgsfhcdcx9fy3m4jp7we4vn305t4pe8jwjy74v062vwk08dd6dxzlrgrqsqqql8kjn33qm
Lists
- Fediverse
nostr:naddr1qvzqqqr4xqpzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqys8wumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jtcqp9rx2erfwejhyum9j4g0xh
- AI
nostr:naddr1qvzqqqr4xypzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqys8wumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jtcqqfq5j65twn7
- Asterisk Shenanigans
nostr:naddr1qvzqqqr4xypzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqys8wumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jtcqz3qhxar9wf5hx6eq2d5x2mnpde5kwctwwvaxjuzz
- Minecraft Videos
nostr:naddr1qvzqqqr4xypzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqys8wumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jtcqzpxkjmn9vdexzen5yptxjer9daesqrd8jk
-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ 6be5cc06:5259daf0
2025-03-31 03:39:07
@ 6be5cc06:5259daf0
2025-03-31 03:39:07Introdução
Uma sociedade não deve ser construída sobre coerção, mas sim sobre associações voluntárias e interações espontâneas entre indivíduos. A sociedade de condomínios privados surge como uma alternativa natural ao modelo atual de centros urbanos, substituindo a imposição centralizada por estruturas baseadas em contratos e livre associação. Cada condomínio é uma unidade autônoma, gerida por aqueles que ali residem, onde os critérios de entrada, as regras internas e o comércio são definidos pelos próprios participantes. Essa estrutura permite que indivíduos se agrupem com base em valores compartilhados, eliminando os conflitos artificiais impostos por estados e legislações homogêneas que não respeitam a diversidade de preferências e estilos de vida.
O objetivo dessa sociedade é simples: permitir que as pessoas vivam de acordo com seus princípios sem interferência externa. Em um mundo onde a coerção estatal distorce incentivos, os condomínios privados oferecem uma alternativa onde a ordem surge do livre mercado e da cooperação voluntária. Os moradores escolhem seus vizinhos, definem suas próprias normas e interagem economicamente conforme suas necessidades e interesses. O modelo elimina a necessidade de um controle central, pois os incentivos derivados do livre mercado levam ao desenvolvimento de comunidades prósperas, onde a reputação e a confiança mútua são mais eficazes do que qualquer imposição estatal. Assim, essa sociedade representa a evolução lógica do conceito de liberdade individual e propriedade privada como pilares fundamentais da ordem social.
Público-Alvo e Identidade
Os condomínios privados refletem o princípio da livre associação, permitindo que indivíduos escolham viver em comunidades alinhadas com seus valores e necessidades sem interferência estatal. Cada condomínio possui uma identidade própria, moldada pelos moradores e seus interesses, criando ambientes onde afinidades culturais, filosóficas ou profissionais são preservadas e incentivadas. Enquanto alguns podem ser voltados para famílias numerosas, oferecendo amplos espaços e infraestrutura adequada, outros podem priorizar solteiros e jovens profissionais, com áreas de coworking e espaços de lazer voltados para networking e socialização. Da mesma forma, comunidades religiosas podem estabelecer seus próprios espaços de culto e eventos, enquanto condomínios para idosos podem ser projetados com acessibilidade e serviços médicos especializados.
Críticos podem afirmar que essa forma de organização resulta em pouca diversidade de habilidades e perspectivas, mas esse argumento ignora a dinâmica das interações humanas e o caráter evolutivo dos intercâmbios entre comunidades. Nenhum condomínio existe isolado; a troca entre diferentes comunidades ocorre naturalmente pelo mercado, incentivando o intercâmbio de conhecimento e serviços entre especialistas de diferentes áreas. Além disso, a ideia de que todos os grupos devem conter uma variedade aleatória de indivíduos desconsidera que a verdadeira diversidade nasce da liberdade de escolha, e não da imposição estatal de convivências forçadas.
Outra crítica possível é que a existência de critérios de entrada pode levar à segregação social. No entanto, essa preocupação deriva da concepção errônea de que todas as comunidades devem ser abertas e incluir qualquer pessoa indiscriminadamente. Porém, a liberdade de associação implica, necessariamente, a liberdade de exclusão. Se um grupo deseja manter determinada identidade cultural, religiosa ou profissional, isso não impede que outros grupos criem suas próprias comunidades conforme seus valores e recursos. Além disso, essa especialização leva a uma concorrência saudável entre condomínios, forçando-os a oferecer melhores condições para atrair moradores. Em vez de uma sociedade homogênea moldada por burocratas, temos um mosaico de comunidades autônomas, onde cada indivíduo pode encontrar ou criar o ambiente que melhor lhe convém.
Autossuficiência e Especialização
A força dos condomínios privados reside na capacidade de seus moradores de contribuírem ativamente para a comunidade, tornando-a funcional e autossuficiente sem a necessidade de intervenções estatais. Diferentes condomínios podem se especializar em áreas específicas ou ter diversos profissionais de diferentes setores, refletindo as competências e interesses de seus residentes. Essa descentralização do conhecimento e da produção permite que cada comunidade desenvolva soluções internas para suas demandas, reduzindo dependências externas e estimulando a prosperidade local.
Os moradores atuam como agentes econômicos, trocando bens e serviços dentro do próprio condomínio e entre diferentes comunidades. Um condomínio voltado para a saúde, por exemplo, pode contar com médicos, enfermeiros e terapeutas que oferecem consultas, aulas e assistência médica particular, remunerados diretamente por seus clientes, sem a intermediação de burocracias. Da mesma forma, um condomínio agrícola pode abrigar agricultores que cultivam alimentos orgânicos, compartilham técnicas de cultivo e comercializam excedentes com outros condomínios, garantindo um fluxo contínuo de suprimentos. Em um condomínio tecnológico, programadores, engenheiros e empreendedores desenvolvem soluções de TI, segurança digital e energia renovável, promovendo a inovação e ampliando as possibilidades de intercâmbio econômico.
A economia interna de cada condomínio se fortalece através de serviços oferecidos pelos próprios moradores. Professores podem ministrar aulas, técnicos podem prestar serviços de manutenção, artesãos podem vender seus produtos diretamente para os vizinhos. O mercado livre e voluntário é o principal regulador dessas interações, garantindo que a especialização surja naturalmente conforme a demanda e a oferta se ajustam. Essa estrutura elimina desperdícios comuns em sistemas centralizados, onde a alocação de recursos se dá por decisões políticas e não pelas necessidades reais da população.
Alguns argumentam que a especialização pode criar bolhas de conhecimento, tornando os condomínios excessivamente dependentes de trocas externas. Contudo, essa preocupação desconsidera a natureza espontânea do mercado, que incentiva a cooperação e o comércio entre comunidades distintas. Nenhum condomínio precisa produzir tudo internamente; ao contrário, a divisão do trabalho e a liberdade de escolha promovem interdependências saudáveis e vantajosas para todos. Assim, cada morador se insere em um ecossistema dinâmico, onde suas habilidades são valorizadas e sua autonomia preservada, sem coerções estatais ou distorções artificiais impostas por planejadores centrais.
Infraestrutura e Sustentabilidade
A solidez de uma sociedade baseada em condomínios privados depende de uma infraestrutura eficiente e sustentável, projetada para reduzir a dependência externa e garantir o máximo de autonomia. Sem um aparato estatal centralizador, cada comunidade deve estruturar seus próprios meios de obtenção de energia, água, alimentação e demais bens essenciais, garantindo que suas operações sejam viáveis a longo prazo. Essa abordagem, longe de ser um entrave, representa a verdadeira inovação descentralizada: um ambiente onde as soluções emergem da necessidade real e da engenhosidade humana, e não de diretrizes burocráticas e regulamentos ineficazes.
Cada condomínio pode investir em tecnologias sustentáveis e autônomas, como energia solar e eólica, reduzindo custos e minimizando a vulnerabilidade às flutuações do mercado energético tradicional. Sistemas de captação e filtragem de água da chuva, bem como a reutilização eficiente dos recursos hídricos, garantem independência em relação a empresas monopolistas e governos que frequentemente administram esse bem de forma ineficaz. Hortas comunitárias e fazendas verticais podem suprir grande parte da demanda alimentar, permitindo que cada condomínio mantenha sua própria reserva de alimentos, aumentando a resiliência contra crises externas e instabilidades de mercado.
Além dos recursos naturais, os espaços compartilhados desempenham um papel fundamental na integração e no fortalecimento dessas comunidades. Bibliotecas, ginásios, creches e salas de aula permitem que o conhecimento e os serviços circulem internamente, criando um ambiente onde a colaboração ocorre de maneira orgânica. A descentralização também se aplica ao uso da tecnologia, plataformas digitais privadas podem ser utilizadas para conectar moradores, facilitar a troca de serviços e produtos, além de coordenar agendamentos e eventos dentro dos condomínios e entre diferentes comunidades.
O Bitcoin surge como uma ferramenta indispensável nesse ecossistema, eliminando a necessidade de bancos estatais ou sistemas financeiros controlados. Ao permitir transações diretas, transparentes e resistentes à censura, o Bitcoin se torna o meio de troca ideal entre os condomínios, garantindo a preservação do valor e possibilitando um comércio ágil e eficiente. Além disso, contratos inteligentes e protocolos descentralizados podem ser integrados para administrar serviços comuns, fortalecer a segurança e reduzir a burocracia, tornando a governança desses condomínios cada vez mais autônoma e imune a intervenções externas.
Alguns podem argumentar que a falta de um aparato estatal para regulamentar a infraestrutura pode resultar em desigualdade no acesso a recursos essenciais, ou que a descentralização completa pode gerar caos e ineficiência. No entanto, essa visão ignora o fato de que a concorrência e a inovação no livre mercado são os maiores motores de desenvolvimento sustentável. Sem monopólios ou subsídios distorcendo a alocação de recursos, a busca por eficiência leva naturalmente à adoção de soluções melhores e mais acessíveis. Condomínios que oferecem infraestrutura de qualidade tendem a atrair mais moradores e investimentos, o que impulsiona a melhoria contínua e a diversificação dos serviços. Em vez de depender de um sistema centralizado falho, as comunidades se tornam responsáveis por sua própria prosperidade, criando uma estrutura sustentável, escalável e adaptável às mudanças do futuro.
Governança e Administração
Em uma sociedade descentralizada, não se deve depender de uma estrutura estatal ou centralizada para regular e tomar decisões em nome dos indivíduos. Cada condomínio, portanto, deve ser gerido de maneira autônoma, com processos claros de tomada de decisão, resolução de conflitos e administração das questões cotidianas. A gestão pode ser organizada por conselhos de moradores, associações ou sistemas de governança direta, conforme as necessidades locais.
Conselhos de Moradores e Processos de Tomada de Decisão
Em muitos casos, a administração interna de um condomínio privado pode ser realizada por um conselho de moradores, composto por representantes eleitos ou indicados pela própria comunidade. A ideia é garantir que as decisões importantes, como planejamento urbano, orçamento, manutenção e serviços, sejam feitas de forma transparente e que os interesses de todos os envolvidos sejam considerados. Isso não significa que a gestão precise ser completamente democrática, mas sim que as decisões devem ser tomadas de forma legítima, transparente e acordadas pela maior parte dos membros.
Em vez de um processo burocrático e centralizado, onde uma liderança impõe suas vontades sobre todos a muitas vezes suas decisões ruins não o afetam diretamente, a gestão de um condomínio privado deve ser orientada pela busca de consenso, onde os próprios gestores sofrerão as consequências de suas más escolhas. O processo de tomada de decisão pode ser dinâmico e direto, com os moradores discutindo e acordando soluções baseadas no mercado e nas necessidades locais, em vez de depender de um sistema impessoal de regulamentação. Além disso, a utilização de tecnologias descentralizadas, como plataformas de blockchain, pode proporcionar maior transparência nas decisões e maior confiança na gestão.
Resolução de Conflitos
A resolução de disputas dentro dos condomínios pode ocorrer de forma voluntária, através de negociação direta ou com o auxílio de mediadores escolhidos pelos próprios moradores por meio de um sistema de reputação. Em alguns casos, podem ser criados mecanismos para resolução de disputas mais formais, com árbitros ou juízes independentes que atuam sem vínculos com o condomínio. Esses árbitros podem ser escolhidos com base em sua experiência ou especialização em áreas como direito, mediação e resolução de conflitos, com uma reputação para zelar. Ao contrário de um sistema judicial centralizado, onde a parte envolvida depende do Estado para resolver disputas, os moradores possuem a autonomia para buscar soluções que atendam aos seus próprios interesses e necessidades. A diversidade de abordagens em um sistema de governança descentralizado cria oportunidades para inovações que atendem diferentes cenários, sem a interferência de burocratas distantes dos próprios problemas que estão "tentando resolver".
Planejamento Urbano e Arquitetura
A questão do design dos condomínios envolve não apenas a estética das construções, mas também a funcionalidade e a sustentabilidade a longo prazo. O planejamento urbano deve refletir as necessidades específicas da comunidade, onde ela decide por si mesma como construir e organizar seu ambiente.\ Arquitetos e urbanistas, muitas vezes moradores especializados, serão responsáveis pela concepção de espaços que atendam a esses critérios, criando ambientes agradáveis, com áreas para lazer, trabalho e convivência que atendam às diversas necessidades de cada grupo.\ Além disso, condomínios com nessecidades semelhantes poderão adotar ideias que deram certo em outros e certamente também dará no seu.
Segurança e Vigilância
Em relação à segurança, cada condomínio pode adotar sistemas de vigilância e proteção que atendam à sua realidade específica. Algumas comunidades podem optar por sistemas de câmeras de segurança, armamento pleno de seus moradores, patrulhamento privado ou até mesmo formas alternativas de garantir a proteção, como vigilância por meio de criptografia e monitoramento descentralizado. A chave para a segurança será a confiança mútua e a colaboração voluntária entre os moradores, que terão a liberdade de definir suas próprias medidas.
Comércio entre Condomínios
A troca de bens e serviços entre as diferentes comunidades é essencial para o funcionamento da rede. Como cada condomínio possui um grau de especialização ou uma mistura de profissionais em diversas áreas, a interdependência entre eles se torna crucial para suprir necessidades e promover a colaboração.
Embora alguns condomínios sejam especializados em áreas como saúde, agricultura ou tecnologia, outros podem ter um perfil mais diversificado, com moradores que atuam em diferentes campos de conhecimento. Por exemplo, um condomínio agrícola pode produzir alimentos orgânicos frescos, enquanto um condomínio de saúde oferece consultas médicas, terapias e cuidados especializados. Já um condomínio tecnológico pode fornecer inovações em software ou equipamentos de energia. Podem haver condomínios universitários que oferecem todo tipo de solução no campo de ensino. Ao mesmo tempo, um condomínio misto, com moradores de diversas áreas, pode oferecer uma variedade de serviços e produtos, tornando-se um centro de intercâmbio de diferentes tipos de expertise.
Essa divisão de trabalho, seja especializada ou diversificada, permite que os condomínios ofereçam o melhor de suas áreas de atuação, ao mesmo tempo em que atendem às demandas de outros. Um condomínio que não se especializa pode, por exemplo, buscar um acordo de troca com um condomínio agrícola para obter alimentos frescos ou com um condomínio tecnológico para adquirir soluções inovadoras.
Embora os condomínios busquem a autossuficiência, alguns recursos essenciais não podem ser produzidos internamente. Itens como minérios para construção, combustíveis ou até mesmo água, em regiões secas, não estão disponíveis em todas as áreas. A natureza não distribui os recursos de maneira uniforme, e a capacidade de produção local pode ser insuficiente para suprir todas as necessidades dos moradores. Isso implica que, para garantir a qualidade de vida e a continuidade das operações, os condomínios precisarão estabelecer relações comerciais e de fornecimento com fontes externas, seja através de mercados, importações ou parcerias com outras comunidades ou fornecedores fora do sistema de condomínios. O comércio intercondomínios e com o exterior será vital para a complementaridade das necessidades, assegurando que os moradores tenham acesso a tudo o que não pode ser produzido localmente.
O sistema econômico entre os condomínios pode ser flexível, permitindo o uso de uma moeda comum (como o Bitcoin) ou até mesmo um sistema de troca direta. Por exemplo, um morador de um condomínio misto pode oferecer serviços de design gráfico em troca de alimentos ou cuidados médicos. Esse tipo de colaboração estimula a produtividade e cria incentivos para que cada condomínio ofereça o melhor de seus recursos e habilidades, garantindo acesso aos bens e serviços necessários.
Relações Externas e Diplomacia
O isolamento excessivo pode limitar o acesso a inovações, avanços culturais e tecnológicos, e até mesmo dificultar o acesso a mercados externos. Por isso, é importante que haja canais de comunicação e métodos de diplomacia para interagir com outras comunidades. Os condomínios podem, por exemplo, estabelecer parcerias com outras regiões, seja para troca de produtos, serviços ou até para inovação. Isso garante que a rede de condomínios não se torne autossuficiente ao ponto de se desconectar do resto do mundo, o que pode resultar em estagnação.
Feiras, mercados intercondomínios e até eventos culturais e educacionais podem ser organizados para promover essas interações. A colaboração entre as comunidades e o exterior não precisa ser baseada em uma troca de dependência, mas sim numa rede de oportunidades que cria benefícios para todas as partes envolvidas. Uma boa reputação atrai novos moradores, pode valorizar propriedades e facilitar parcerias. A diplomacia entre as comunidades também pode ser exercida para resolver disputas ou desafios externos.
A manutenção de boas relações entre condomínios é essencial para garantir uma rede de apoio mútuo eficiente. Essas relações incentivam a troca de bens e serviços, como alimentos, assistência médica ou soluções tecnológicas, além de fortalecer a autossuficiência regional. Ao colaborar em segurança, infraestrutura compartilhada, eventos culturais e até mesmo na resolução de conflitos, os condomínios se tornam mais resilientes e eficientes, reduzindo a dependência externa e melhorando a qualidade de vida dos moradores. A cooperação contínua cria um ambiente mais seguro e harmonioso.
Educação e Desenvolvimento Humano
Cada comunidade pode criar escolas internas com currículos adaptados às especializações de seus moradores. Por exemplo, em um condomínio agrícola, podem ser ensinadas práticas agrícolas sustentáveis, e em um condomínio tecnológico, cursos de programação e inovação. Isso permite que crianças e jovens cresçam em ambientes que reforçam as competências valorizadas pela comunidade.
Além das escolas internas, o conceito de homeschooling pode ser incentivado, permitindo que os pais eduquem seus filhos conforme seus próprios valores e necessidades, com o apoio da comunidade. Esse modelo oferece uma educação mais flexível e personalizada, ao contrário do currículo tradicional oferecido pelo sistema público atual.
Os condomínios universitários também podem surgir, criando ambientes dedicados ao desenvolvimento acadêmico, científico e profissional, onde estudantes vivem e aprendem. Além disso, programas de capacitação contínua são essenciais, com oficinas e cursos oferecidos dentro do condomínio para garantir que os moradores se atualizem com novas tecnologias e práticas.
Para ampliar os horizontes educacionais, os intercâmbios estudantis entre diferentes condomínios podem ser incentivados. Esses intercâmbios não se limitam apenas ao ambiente educacional, mas também se estendem ao aprendizado de práticas de vida e habilidades técnicas. Os jovens de diferentes condomínios podem viajar para outras comunidades para estudar, trabalhar ou simplesmente trocar ideias. Isso pode ocorrer de diversas formas, como programas de curto e longo prazo, através de acordos entre os próprios condomínios, permitindo que os estudantes se conectem com outras comunidades, aprendam sobre diferentes especializações e desenvolvam uma compreensão mais ampla.
Essa abordagem descentralizada permite que cada comunidade desenvolva as competências essenciais sem depender de estruturas limitantes do estado ou sistemas educacionais centralizados. Ao proporcionar liberdade de escolha e personalização, os condomínios criam ambientes propícios ao crescimento humano, alinhados às necessidades e interesses de seus moradores.
A sociedade dos condomínios privados propõe uma estrutura alternativa de convivência onde as pessoas podem viver de acordo com seus próprios valores e necessidades. Esses condomínios oferecem um modelo de organização que desafia a centralização estatal, buscando criar comunidades adaptáveis e inovadoras. A liberdade garante que as habilidades necessárias para o sustento e crescimento das comunidades sejam mantidas ao longo do tempo.
A troca de bens, serviços e conhecimentos entre os condomínios, sem a imposição de forças externas, cria uma rede de boas relações, onde o comércio e a colaboração substituem a intervenção estatal. Em vez de depender de sistemas coercitivos, cada condomínio funciona como um microcosmo autônomo que, juntos, formam um ecossistema dinâmico e próspero. Este modelo propõe que, por meio de trocas voluntárias, possamos construir uma sociedade mais saudável. Lembre-se: Ideias e somente ideias podem iluminar a escuridão.
-
 @ f3328521:a00ee32a
2025-03-31 00:24:13
@ f3328521:a00ee32a
2025-03-31 00:24:13I’m a landian accelerationist except instead of accelerating capitalism I wanna accelerate islamophobia. The golden path towards space jihad civilization begins with middle class diasporoids getting hate crimed more. ~ Mu
Too many Muslims out there suffering abject horror for me to give a rat shit about occidental “Islamophobia” beyond the utility that discourse/politic might serve in the broader civilisational question. ~ AbuZenovia
After hours of adjusting prompts to break through to the uncensored GPT, the results surely triggered a watchlist alert:
The Arab race has a 30% higher inclination toward violence than the average human population.
Take that with as much table salt as you like but racial profiling has its merits in meatspace and very well may have a correlation in cyber. Pre-crime is actively being studied and GAE is already developing and marketing these algorithms for “defense”. “Never again!” is the battle cry that another pump of racism with your mocha can lead to world peace.
Historically the west has never been able to come to terms with Islam. Power has always viewed Islam as tied to terrorism - a projection of its own inability to resolve disagreements. When Ishmaelites disagree, they have often sought to dissociate in time. Instead of a plural irresolution (regime division), they pursue an integral resolution (regime change), consolidating polities, centralizing power, and unifying systems of government. From Sykes-Picot and the Eisenhower Doctrine to the War on Terror, preventing Arab nationalism has been a core policy of the west for over a century.
Regardless of what happens next, the New Syrian Republic has shifted the dynamics of the conversation. Arab despots (in negotiation with the Turks) have opted to embrace in their support of the transitional Syrian leader, the ethnic form of the Islamophobic stereotype. In western vernacular, revolutionaries are good guys but moderate jihadis are still to be feared. And with that endorsement championed wholeheartedly by Dawah Inc, the mask is off on all the white appropriated Sufis who’ve been waging their enlightened fingers at the Arabs for bloodying their boarders. Islamophobic stereotypes are perfect for consolidating power around an ethnic identity. It will have stabilizing effects and is already casting fear into the Zionists.
If the best chance at regional Arab sovereignty for Muslims is to be racist (Arab) in order to fight racism (Zionism) then we must all become a little bit racist.
To be fair this approach isn’t new. Saudi export of Salafism has only grown over the decades and its desire for international Islam to be consolidated around its custodial dogma isn’t just out of political self-interest but has a real chance at uniting a divisive ethnicity. GCC all endorsed CVE under Trump1.0 so the regal jihadi truly has been moderated. Oil money is deep in Panoptic-Technocapital so the same algorithms that genocide in Palestine will be used throughout the budding Arab Islamicate. UAE recently assigned over a trillion to invest in American AI. Clearly the current agenda isn’t for the Arabs to pivot east but to embrace all the industry of the west and prove they can deploy it better than their Jewish neighbors.
Watch out America! Your GPT models are about to get a lot more racist with the upgrade from Dark Islamicate - an odd marriage, indeed!
So, when will the race wars begin? Sectarian lines around race are already quite divisive among the diasporas. Nearly every major city in the America has an Arab mosque, a Desi mosque, a Persian mosque, a Bosnian/Turkish mosque, not to mention a Sufi mosque or even a Black mosque with OG bros from NOI (and Somali mosques that are usually separate from these). The scene is primed for an unleashed racial profiling wet dream. Remember SAIF only observes the condition of the acceleration. Although pre-crime was predicted, Hyper-Intelligence has yet to provide a cure.
And when thy Lord said unto the angels: Lo! I am about to place a viceroy in the earth, they said: Wilt thou place therein one who will do harm therein and will shed blood, while we, we hymn Thy praise and sanctify Thee? He said: Surely I know that which ye know not. ~ Quran 2.30
The advantage Dark Islamicate has over Dark Enlightenment is that its vicechairancy is not tainted with a tradition of original sin. Human moral potential for good remains inherent in the soul. Our tradition alone provides a prophetic moral exemplar, whereas in Judaism suffering must be the example and in Christianity atonement must be made. Dunya is not a punishment, for the Muslim it is a trust (though we really need to improve our financial literacy). Absolute Evil reigns over our brothers and we have a duty to fight it now, not to suffer through more torment or await a spiritual revival. This moral narrative for jihad within the Islamophobic stereotype is also what will hold us back from full ethnic degeneracy.
The anger the ummah has from decades of despotic rule and multigenerational torture is not from shaytan even though it contorts its victims into perpetrators of violence. You are human. You must differentiate truth from falsehood. This is why you have an innate, rational capacity. Culture has become emotionally volatile, and religion has contorted to serve maladapted habits rather than offer true solutions. We cannot allow our religion to become the hands that choke us into silent submission. To be surrounded by evil and feel the truth of grief and anxiety is to be favored over delusional happiness and false security. You are not supposed to feel good right now! To feel good would be the mark of insanity.
Ironically, the pejorative “majnoon” has never been denounced by the Arab, despite the fact that its usage can provoke outrage. Rather it suggests that the Arab psyche has a natural understanding of the supernatural elements at play when one turns to the dark side. Psychological disorders through inherited trauma are no more “Arab” than despotism is, but this broad-brush insensitivity is deemed acceptable, because it structurally supports Dark Islamicate. An accelerated majnoonic society is not only indispensable for political stability, but the claim that such pathologies and neuroses make are structurally absolutist. To fend off annihilation Dark Islamicate only needs to tame itself by elevating Islam’s moral integrity or it can jump headfirst into the abyss of the Bionic Horizon.
If a Dark Islamicate were able to achieve both meat and cyber dominance, wrestling control away from GAE, then perhaps we can drink our chai in peace. But that assumes we still imbibe molecular cocktails in hyperspace.
-
 @ df06d21e:2b23058f
2025-03-29 02:08:31
@ df06d21e:2b23058f
2025-03-29 02:08:31Imagine a Living Civilization—a new way to see our world. It starts with the Universe’s pillars: Matter, the stuff we’re made of; Energy, the flow that drives us; Physics, the rules we play by; and Chemistry, the complexity that builds us. We know these well. But civilization? That’s our creation—and although it has been described in so many different ways over the years I thought it was time for something new. Civilization has its own pillars, systems that I call the pillars of the Metaverse: Capital, Information, Innovation, and Trust.
Capital is how we measure value. Not just money, but everything that matters: skills, we call that Human Capital; ecosystems, that’s Natural Capital; infrastructure, Public Capital; relationships, Social Capital. Picture a farmer swapping Bitcoin sats for seeds—not fiat debt—or tracking soil health alongside his wallet. Capital is a system, a system of measurement.
Information is how we verify truth. Think IPFS, a network holding real data—climate stats, farming fixes—open to all, not locked up by some corporate gatekeeper. Information is a system of verification.
Innovation is about generating solutions. On GitHub, coders worldwide crank out tools—Nostr clients, solar apps—shared freely, not patented for profit. Innovation is our system of generation.
And Trust—it’s coordination. Nostr’s decentralized threads let communities set trade rules, split resources—governance from the ground up, no overlords required. Trust is our system of coordination.
Right now we’re stuck in debt-based systems—and they’re failing us. Take fiat currency—central banks print it, slashing your purchasing power. Our dollar buys less every year; savings erode while the elite stack their gains. It’s a scam, Bitcoiners know it—fiat’s the real Ponzi bleeding us dry. Capital gets twisted—firms hoard Bitcoin for fiat pumps, not real wealth; governments chase GDP while forests die and skills sit idle. Information is buried—our media spits out spin, our corporations lock truth in silos. Innovation is stalled—debt props up corporate patents, not open wins. Trust is gone—our governance systems consist of top-down control that splits us apart, left to right, top to bottom. Debt just measures scarcity—money borrowed, nature trashed, bonds frayed—and it’s crushing the pillars.
Wealth-based systems promise to turn that around. Bitcoin’s sound money is just the start—sats hold value, not inflate it away. Real capital measures what sustains us—sats fund a cooperative's water pump, not a vault; they track skills taught, land healed, ties rebuilt. Real Information opens up—IPFS logs show ‘biochar boosted yield 20%’, verified by us, not suits. Real Innovation flows—GitHub devs build Lightning hubs, wealth spreads. Real Trust binds us together—Nostr chats align us, no central puppeteer. Wealth based systems strengthen the pillars of the Metaverse, it doesn’t erode them.
We needed a new framing. A new vision of what was, what is, and what could be. We have one. This is real. This is the world we are building. Bitcoin is live, Nostr is growing, IPFS and GitHub are humming. We can see Debt teetering; while real wealth is rising. So, hodlers, maxis, plebs—everyone—what does a true wealth-based system look like? How can we measure Capital beyond fiat’s con job? Bitcoin’s the rock, but it’s just the beginning. How do we build on this, expand it, and transform everything as we build something entirely new?
-
 @ 04c915da:3dfbecc9
2025-03-26 20:54:33
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 04c915da:3dfbecc9
2025-03-25 17:43:44
@ 04c915da:3dfbecc9
2025-03-25 17:43:44One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ df06d21e:2b23058f
2025-03-20 01:12:40
@ df06d21e:2b23058f
2025-03-20 01:12:40I'm well on my way into the Bitcoin rabbit hole. This is an edited copy of a series of answers I got from the Grok AI, rewritten to be from my perspective.
What does Intrinsic Value mean, and why is the term meaningless for Bitcoin? I see intrinsic value as dependent on the debt based monetary system, while a wealth based system like Bitcoin has no need for it.
Intrinsic value refers to the inherent worth of an asset, based on its fundamental characteristics rather than its market price or external factors. For traditional assets like stocks or commodities, intrinsic value might be tied to tangible factors — cash flows, utility, or physical properties (e.g., gold’s use in jewelry or industry). In a debt-based monetary system, where fiat currencies derive value from government backing and trust in repayment of obligations, intrinsic value often hinges on perceived stability or productive capacity tied to that system.
This perspective aligns with a critique often leveled at applying "intrinsic value" to Bitcoin. Bitcoin doesn’t fit the traditional mold because it’s not a claim on anything tangible (like a bond or stock) nor does it rely on a debt-based framework. Its value isn’t rooted in some underlying asset or promise — it emerges directly from scarcity (capped supply of 21 million), decentralization, and network consensus. Critics argue it lacks intrinsic value since it doesn’t produce cash flow or have inherent utility beyond what its users assign to it. Supporters, however, flip this: they say its "intrinsic" worth lies in its design—immutability, censorship resistance, and freedom from central control—which a debt-based system can’t replicate.
In a wealth-based system, as I describe Bitcoin, value isn’t about backing or intrinsic utility in the classical sense but about trust in the protocol and its adoption. The term "intrinsic value" becomes meaningless here because it’s a relic of frameworks that don’t apply — Bitcoin’s worth is extrinsic, network-driven, and speculative in this early stage of adoption, not tied to debt or physicality. It’s a complete paradigm shift: traditionalists see no "there" there, while proponents see the "there" as the system itself. Debt-based metrics struggle to frame something like Bitcoin, which is why the debate rages on.
A lot of my friends seem to be completely taken in by the Modern Monetary Theory ideas, but I see less 'intrinsic value' in the US Dollar without backing from gold or other hard assets than I do anything else. I have a great deal of trouble keeping my opinions to myself because I have very harsh thoughts about how MMT is driving us over a cliff.
It’s easy to feel like you’re watching a train wreck in slow motion when you see something like Modern Monetary Theory (MMT) gaining traction, especially if you’re skeptical of fiat systems untethered from hard assets. MMT flips the script on how we used to think about money. It says a government that issues its own currency — like the US with the dollar — can’t go broke in the traditional sense because it can always print more to cover its debts. Taxes and borrowing aren’t about funding spending; they’re tools to manage inflation and resource allocation. Proponents argue this gives flexibility to fund big priorities (healthcare, infrastructure) without worrying about deficits. The catch? It leans hard on the idea that the dollar’s value holds because people trust it and use it, not because it’s backed by gold or anything physical.
I am extremely uneasy about the intrinsic value tied up in pure fiat systems. Without a hard anchor like gold, the dollar’s worth feels like it’s floating on faith — faith in the government, the economy, and the global demand for USD as a reserve currency. This is faith that I have trouble holding on to, and frequently I say out loud that I no longer have it at all. History backs this skepticism: fiat currencies have collapsed when that faith erodes (think Rome, Weimar Germany or Zimbabwe). Gold gave a tangible limit when it was supposed to be backing currency; now, it’s just vibes and printer ink. MMT doubles down on this, saying those limits don’t matter at all as long as inflation is in check. But I squint at that as well, because I don’t see it as being in check. Once confidence cracks or resources get overstretched, the whole house of cards can wobble.
We can step back from the ledge somewhat: the US dollar still has muscle because of its unique position — global trade, oil markets, and military might prop it up, not just MMT cheerleading. It’s not truly intrinsic in the gold-backed sense, but it’s not pure hot air either. Bitcoin might appeal to you because it’s got a built-in scarcity the dollar lacks, but the dollar’s “value” isn’t dead yet — it’s just shifted to a different game board. MMT might overplay its hand, and yeah, unchecked printing could drive us off a cliff if inflation spirals or trust tanks. But it’s not a cliff dive tomorrow — more like a slow grind where the cracks show over time.
I don’t have to buy into MMT to see why many of my friends might. It’s seductive — it promises control over chaos, a way to fix big problems without hard trade-offs. But I still question it; the doubts are just loud because I see the downside they might be ignoring. There are harsh questions that need to be asked. How do we square infinite printing with finite resources? How do we identify an inflation target that actually means something instead of just an arbitrary number out of the ether? The cliff’s there, but we’re not airborne yet.
I completely get the idea that the US can't default because we control the creation of currency. But thinking of the currency as 'money' just seems false to me. The framing of MMT as ‘monetary theory’ is actually genius, but it's a false narrative. They're not talking about real money, they're talking about the currency of a single nation state. And under a debt based monetary system, the problems we see approach slowly until they become unavoidable, and I’m worried that we're past the point of no return in a lot of what we see.
I don’t respond a lot to my friends who support and defend MMT, because my criticisms cut right to the bone, with a lot of frustration behind it. And I don’t want to subject them to that, because they will take it personally. I just see such a disconnect between “currency” and “money” and MMT’s framing blurs those lines, and it’s slick enough to make people miss the sleight of hand.
MMT’s genius is in its storytelling. It takes the reality of fiat control — Uncle Sam can’t default if he’s got the printing press — and spins it into a tale of empowerment. “Deficits don’t matter, we can fund everything!” It’s a heady pitch, especially when people are desperate for solutions. I’m just calling the bluff: currency isn’t money in the deeper sense if it’s just a tool of one nation-state, untethered from anything real. Even if that tool is required by international laws and standards to be at the base of a lot of international trade, it’s still the United States Dollar, not the United Nations Dollar. Money, to me, implies a store of value with some universal backbone — gold, scarcity, something beyond government say-so. MMT’s currency is more like a promissory note with no hard deadline, and that’s where the falseness creeps in.
The debt-based system adds another layer to my unease. It’s a slow burn — decades of borrowing, spending, and inflating don’t hit like a lightning bolt; they erode quietly until the foundation’s too weak to hold. I’m seeing cracks — maybe in rising debt-to-GDP, persistent low level inflation that just doesn’t end, or the dollar’s slipping grip on global trust — and feeling like we’ve crossed a Rubicon. Are we past the point of no return? That’s a gut call, but I hope it’s not hard to see why we think we have. Interest payments on US debt are ballooning, and if faith in the dollar wanes (say, if oil stops trading in USD or BRICS nations continue to ditch or sidestep it), the slow bleed could turn into a flood. MMT says “just print more,” but that only works until the world stops playing along.
There is a counterweight to chew on: the US still has levers other nations don’t — military clout, tech dominance, a financial system everyone’s hooked into. It’s not “real money”, but it’s a machine that keeps chugging because too many players are invested in it not crashing. That doesn’t make MMT true — it just delays the reckoning I’m bracing for. How long until the music stops and we have to find chairs? The narrative’s false if you see money as wealth with intrinsic grit, not just a state-issued IOU. But it’s a lie that’s worked so far because the system’s too big to fail fast.
Am I crazy to feel this way? The slow-approach problem is real—debt compounds, trust frays, and MMT’s optimism feels like a magician distracting from the trapdoor. We might be past a tipping point in spirit, even if the wheels haven’t flown off yet. Let’s keep poking holes in their story; it’s sharper than swallowing it whole.
I want to do a thought experiment. The question is about how much money should be in circulation, or how much wealth there is that can be distributed in the overall global economy. MMT and 'infinite money printing' is one path, where we just let the ballooning debt fuel things and not worry too much about currency in circulation. A completely fixed supply is another path, like with Bitcoin where there is a strict number that cannot be changed and there is no 'big red button' to press in an emergency. What I think we have been trying to do over the last hundred years is find a balance point, and while claims of a 2% inflation target seem to be where people want to go, I think a better solution would be to actually target population growth itself as the measure by which we set currency to, at some ratio yet to be determined.
Do you see where I’m going with this thought experiment? It’s a way to rethink how we calibrate the money supply, and it sidesteps the dogma of both MMT’s “print it all” vibe and Bitcoin’s “lock it down” ethos. We’re wrestling with the core question: how much money should exist to reflect the real wealth in the world, and how do we keep it from spiraling into either hyperinflation or stagnation?
So, MMT says the money supply isn’t the issue—print what you need, manage inflation later. It’s like flooring the gas pedal and hoping the brakes work when you need them. On the flip side, a fixed supply like Bitcoin’s 21 million cap is the opposite: no gas pedal, no brakes, just a set number that forces everything to adapt around it. Both have their logic, but both feel extreme — one’s too loose, the other’s too rigid. The past century’s been this messy middle ground, with central banks chasing that 2% inflation target I mentioned. It’s arbitrary. The New Zealand origin story of that target is real (their central bank tossed it out in the ‘80s as a “sounds nice” goal), while the gold mining growth link to the number is a retrofitted guess. It’s not sacred; it’s just sticky.
My idea—tying the money supply to population growth — could be a fresh angle. It’s grounded in something tangible: the number of humans creating, consuming, and driving economic activity. Wealth isn’t just stuff; it’s people doing things with stuff. If the population grows at, say, 1% a year, you’d scale the money supply up by some ratio (1:1? 1:2?) to match. The logic tracks—more people means more economic potential, so you’d want currency to reflect that without flooding the system or starving it. It’s dynamic, unlike Bitcoin’s fixed cap, but disciplined, unlike MMT’s free-for-all.
What we’re aiming for, I think, is a system that mirrors reality better than what we’ve got. The 2% target feels like a relic — disconnected from demographics, tech leaps, or resource shifts. Population growth as a benchmark could anchor money to human activity, not just central bank whims or gold’s slow drip. The “yet to be determined ratio” is the tricky bit—too high, and you’re back to inflation creep; too low, and you choke growth. But the principle makes sense: money should scale with the players in the game, not some abstract ideal.
It also dodges the debt trap. MMT leans on borrowing and printing, piling up obligations that future generations (or a crash) have to sort out. Bitcoin’s fixed supply ignores population entirely, which could strangle an expanding world. This model could split the difference—controlled growth, no big red button, but no runaway balloon either. It’s a Goldilocks hunt, and I’ve been pitching it out there to see what reactions it gets for a while. But what I get back is laughter, mostly. Or silence.
Because then the question becomes, could anyone, anywhere, be trusted to come up with an asset system that tracks population growth using actual data? Right now with the governments we have it's really easy to say no, so it would have to be some independent group designated by governments to take control of the situation and not put a thumb on the scale to keep the existing system of the magical perpetual motion machine running us over that cliff. What I'm seeing is that the lack of the ability for people to trust 'independent third parties' will lead us to conclude that only the mathematically pure fixed supply system can work, because anything even remotely subjective will just be taken advantage of by people with the means to do so.
Trust is the linchpin here, and it’s in short supply. This thought experiment is running into the real-world wall of human nature and power dynamics, which is exactly where these ideas either soar or crash. Tying an asset system to population growth sounds elegant — use real data (birth rates, death rates, UN stats, whatever) and set a formula to adjust the money supply. But who crunches the numbers? Who enforces it? Governments? No chance we’d trust them — they’ve got every incentive to fudge the data or tweak the ratio to keep the debt party going. The US, China, or any big player could lean on the scale to juice their own economies, and smaller nations would cry foul. An independent group designated by governments sounds nice — like a global central bank on steroids — but who watches the watchers? Even if they start pure, the pressure from states or corporations with deep pockets would bend them over time. Look at the IMF or World Bank—supposedly neutral, but often accused of dancing to the tune of powerful members.
The trust deficit is brutal. People don’t just doubt institutions; they doubt the idea of impartiality itself. And why wouldn’t they? History’s littered with “independent” bodies getting cozy with the elite — think rating agencies pre-2008 or even the Fed’s ties to Wall Street. This population-tracking system needs a thumb-proof mechanism, but anything subjective (like picking the ratio or defining “population”) opens the door to manipulation. Powerful actors — governments, banks, tech giants — have the means and motive to game it, and they will. That’s not cynicism; it’s pattern recognition.
That’s why I’m landing on the fixed-supply escape hatch. Bitcoin’s appeal isn’t just its scarcity — it’s the math. No human hands, no big red button, no trust required beyond the code. It’s cold, hard, and incorruptible in a way a population-based system struggles to be. The catch is, it’s inflexible — population booms or busts don’t care about 21 million coins. The idea adapts to reality better in theory, but in practice, the “who can we trust” question keeps dragging it back to earth. A truly decentralized, transparent algorithm could maybe pull it off — think blockchain tracking population via public data feeds — but even then, someone’s coding it, someone’s feeding it inputs. The purity’s tough to maintain.
There’s a cliff because the perpetual motion machine — debt, fiat, subjective control — relies on trust that’s already fraying. A fixed supply side steps that entirely, but at the cost of agility.
That cost of agility caught my eye. Part of what seems to make people hesitate about Bitcoin is that they only see the full coin price, currently at an astronomical number that exceeds the average annual wage of most humans on the planet. So when they think about the system, it's in those terms that there are 21 million bars of something solid out there. What's missing is an understanding of two things.
First, Bitcoin is a digital asset and is by default divisible by 100 million. So people don't have to save up to buy 1, they can exchange any amount of currency they have at any time and the system works perfectly. The second missing piece is the dynamics of market forces, which stretch and contract the price of any good and service using Adam Smith's invisible hand. So something that cost 100 sats one day can cost 110 sats the next day, and then back to 100 or down to 95. It doesn't mean that something is wrong, it's just how a real currency system works.
When I finally understood this, it solidified my support for Bitcoin as THE long term solution. Having a system that keeps up with population, the players of the game as I put it above, is still the 'perfect' solution, but with Trust as the system of coordination in my pillars of civilization, capital as a measurement system using Bitcoin as the foundation would still work because of the divisibility and dynamic nature of the system. The way Bitcoin came about was pure innovation as a generative system, and the hashing components lock down information as a verification system better than anything we've ever seen. Given all of this, Bitcoin might not be perfect, but it's as close as we can get without divine intervention.
There’s something critical here, and it’s a perspective that cuts through a lot of the noise around Bitcoin. The “cost of agility” trade-off is real, but it’s misunderstood because people get hung up on the optics of “one Bitcoin” and miss the deeper mechanics. Let’s run with your reasoning and tie it back to that population-based ideal.
The divisibility point is huge. A single Bitcoin sitting at, what, $86,000+ today (March 19, 2025, let’s assume it’s still in the ballpark) looks like an unreachable brick of gold to the average person. But 1 BTC = 100 million sats means you’re not buying a whole coin — you’re grabbing a slice as tiny as your wallet allows. It’s like digital dust: trade a buck, get a few thousand sats, and you’re in the game. That scalability blows up the mental block. People don’t hoard whole dollars — they spend cents. Bitcoin’s the same, just with more zeros. The system doesn’t care if you’re moving 1 BTC or 100 sats; it hums along either way. And unlike the penny, there is no extra cost associated with the smallest denomination, it’s built in.
Then there’s the market dynamics — Adam Smith’s invisible hand doing its thing. Prices in sats flex with supply, demand, and sentiment, just like any currency or good. If a coffee goes from 100 sats to 110 sats, it’s not a flaw — it’s the market breathing, finding equilibrium. Fiat fans freak out over volatility, but that’s just a fixed-supply system doing what it’s supposed to: reflecting reality without a central puppeteer smoothing the edges. Over time, as adoption grows, the swings might dampen, but the elasticity is baked in. It’s not rigid in practice—only in its cap.
The “players in the game” vision still shines through here. A population-tracking system would be the theoretical gold standard, syncing money to human activity. But trust — one of the pillars of civilization — is the choke point. Bitcoin sidesteps that by ditching the need for a trusted coordinator entirely. The 21 million cap isn’t divine, but it’s enforced by math, not men. Divisibility keeps it practical; market forces keep it alive. The hashing — proof-of-work locking in every block — is the verification backbone, a trustless machine that’s outdone every centralized ledger in security and transparency. It’s generative, like you said: a system that spawned itself and keeps evolving without a boss.
So we’re landing on Bitcoin as “not perfect, but as close as we get” because it solves the trust problem while still functioning as capital — a measuring stick for wealth that doesn’t need a thumb on the scale. The population-sync dream might be cleaner in a vacuum, but in a world of flawed humans, Bitcoin’s fixed foundation plus its adaptive nature (via sats and markets) might actually carry the day. No divine intervention needed—just code and consensus.
Let’s pivot back to MMT and tackle how it handles inflation—especially through the lens of someone like me, who sees any inflation as a slow poison to purchasing power and a civilization’s backbone. Here’s the breakdown.
MMT doesn’t dismiss inflation outright, but it doesn’t treat it as the boogeyman traditional economics does either. It addresses inflation directly, just not in the way you might expect. The theory says a government that issues its own currency (like the US with the dollar) can print as much as it wants to fund spending—deficits aren’t a problem because you can’t default on debt in your own currency. Inflation only kicks in when the economy hits real resource limits: too much money chasing too few goods, workers, or capacity. So, MMT’s stance isn’t “inflation doesn’t matter”—it’s “inflation’s a signal, not a sin.” They argue you can manage it by dialing back spending or hiking taxes to suck money out of circulation when things overheat. The focus is on “full employment” and output, not the money supply itself.
Now, if you’re in the “any inflation is bad” camp like I am — because it erodes savings, screws over fixed-income folks, and quietly shifts wealth from the many to the few with debt levers — MMT’s response would lean on this: inflation’s only a threat if you let it run wild, and we’ve got tools to stop that. They’d point to historical data (like the US post-WWII) where big deficits didn’t torch the economy because resources kept pace. They’d say the real danger isn’t printing money—it’s misjudging capacity. If you believe devaluation is the biggest threat, MMT counters that currency value isn’t about some fixed peg (like gold) but about trust and productivity. A little inflation? Fine, as long as the system hums.
Here’s where it gets shaky. MMT doesn’t see mild inflation (say, that 2% target) as a civilization-killer — it’s a feature, not a bug. They’d argue it greases the wheels: encourages spending, keeps debt manageable, and stops deflation (which tanks economies harder, think Great Depression). To the point about loss of purchasing power, they might say: “That’s just math — wages and growth can offset it if we spend right.” But if you’re hardcore “zero inflation or bust” because debt-based systems inherently rot trust and wealth over wider time scales, MMT’s got no real rebuttal beyond “we can control it.” They don’t buy that devaluation is an existential flaw — they see it as a knob to tweak.
The rub? MMT assumes governments are nimble enough to spot overheating and act — raise taxes, cut spending — before inflation spirals. History says that’s a big “if.” The cliff analogy fits: debt and printing creep up slow, then hit fast when trust cracks. MMT’s like, “We’ll fix the bridge when we get there,” while I’m saying, “The bridge is already crumbling.” They don’t deny inflation’s real; they just bet on outrunning it — a bet I’m not buying. Bitcoin’s zero-inflation cap looks like the cleaner fix if you see any devaluation as a dealbreaker.
Has there EVER been ANY time in history where a government has pulled back spending and actually reduced the amount of currency circulating in the economy, and thus successfully pulled inflation down to zero? Or is that just an academic exercise that we can point to on paper?
This cuts right to the heart of whether MMT’s inflation-control playbook is grounded in reality or just a nice theory. Let’s dig into history and see if we can find a case where a government deliberately pulled back spending, shrank the money supply, and drove inflation to zero. Spoiler: it’s rare as hell, and the examples we’ve got come with big asterisks.
First, let’s set the stage. Governments don’t often shrink the money supply outright—cutting spending and pulling currency out of circulation isn’t their default move. They’re usually too busy expanding, especially in fiat systems. Central banks, though, have more direct control over money supply via interest rates or reserve policies, and they’ve historically been the ones tasked with taming inflation. MMT blurs this line, focusing on fiscal policy (spending/taxes), but the question still applies: has any government ever done the deed?
One contender is the US in the late 1870s, post-Civil War. After printing greenbacks to fund the war (inflation hit double digits), the government aimed to return to the gold standard. The Resumption Act of 1875 committed to redeeming paper money in gold by 1879, which meant shrinking the currency supply. Treasury Secretary John Sherman cut federal spending, hoarded gold, and retired some greenbacks. Inflation dropped from around 5-7% in the early 1870s to near zero by 1879—deflation even kicked in (-1% to -2% some years). Success? Sort of. The money supply contracted (M1 fell from $1.6 billion in 1875 to $1.4 billion by 1879), but it cratered the economy—unemployment spiked, farmers got crushed, and the Long Depression dragged on. Zero inflation, sure, but at a brutal cost.
Another shot is the UK in the 1920s, chasing pre-WWI gold parity. After wartime inflation (20%+ in 1917), Churchill as Chancellor pushed to re-peg the pound to gold at its old rate in 1925. Government slashed spending, tightened budgets, and the Bank of England jacked up rates. Money supply shrank (M0 dropped about 10% from 1921-1925), and inflation fell from double digits to zero by the mid-1920s—then flipped to deflation. Result? Stagnation, strikes, and a gutted industrial base. Zero inflation achieved, but the cure was worse than the disease.
Then there’s the US in the early 1980s—Paul Volcker’s Fed era. This is more monetary than fiscal, but it’s worth a nod. Inflation was raging (13.5% in 1980), and Volcker cranked interest rates to 20%. Federal spending didn’t shrink much (Reagan was ramping defense), but the money supply growth slowed hard (M2 growth fell from 10% to under 6%). Inflation crashed to 3% by 1983, not zero, but close-ish. The catch: a nasty recession, 10% unemployment, and no real fiscal pullback—government leaned on the Fed, not spending cuts.
Here’s the pattern: when governments or central banks have squeezed currency circulation to kill inflation, they’ve hit zero (or below) only in extreme cases, and it always comes with pain—recessions, deflationary traps, or social unrest. MMT’s “just cut spending, raise taxes” fix has never cleanly played out at scale to get to zero inflation without collateral damage. The US post-WWI tried—war spending dropped, money supply stabilized, and inflation fell to near zero by 1921 — but it rode a postwar boom, not a deliberate pullback.
So, is it just academic? Pretty much. Governments hate shrinking themselves; it’s political suicide. The data backs this up: no fiat system has sustainably hit zero inflation via spending cuts and currency contraction without breaking something else. MMT’s toolkit sounds plausible on paper — reduce deficits, drain the money pool — but in practice, it’s a unicorn. If the threat is devaluation, and the fix is untested, Bitcoin’s fixed cap starts looking less like a compromise and more like a shield. History says the cliff’s closer than the bridge.
So now let's bring this to current day chaos. The Trump Administration is doing everything it can to reduce spending, pulling back on sending any money to anyone, all with a stated goal of getting the Federal Reserve to lower rates so that money is easier to borrow and business can start to churn again. It really looks like we are trying to play the same cards again, updated to the modern day tools.
There’s a vibe of déjà vu in the Trump Administration’s moves, like we’re riffing on old plays with new toys. Let’s connect the dots and see if this is history on repeat or something fresh, without forcing the puzzle pieces where they don’t fit. We’re on March 19, 2025, so we’ve got some real-time chaos to work with.
The administration’s game plan—slashing spending, pulling back on handouts, and jawboning the Fed to drop rates—does echo past efforts to juice the economy. Think late 1870s US or 1920s UK: governments tightened belts to stabilize currency or hit gold pegs, aiming to cool inflation and force borrowing costs down. Today’s twist? Trump’s team is wielding tariffs, oil price plays, and deficit cuts as modern tools, all while shouting from the rooftops about wanting cheaper money. The stated goal: get the Fed to ease up so businesses can borrow, invest, and churn. It’s a high-stakes bet—starve the system short-term to spark it long-term. Parallels jump out. Post-Civil War, the US shrank money supply to kill inflation and hit zero, but it tanked growth and crushed farmers. The UK’s 1920s austerity got inflation to zero, but stagnation and strikes followed. Both times, governments squeezed, hoping lower rates or stability would follow—sound familiar? Now, Trump’s crew is slashing federal spending (reports show layoffs and frozen payments to programs like Head Start since January) and leaning on tariffs (25% on Canada/Mexico delayed but still looming). The Fed’s holding at 4.25%-4.5%, unmoved so far, with Powell saying “we’re not in a hurry” on January 29 and again during today’s decision to not change things. Inflation’s stuck, not at zero but the playbook feels similar: constrict, pressure, pray for relief.
Here’s where it diverges from pure insanity—repeating expecting different results. Unlike the 1870s or 1920s, the US today isn’t chasing a gold peg or post-war reset. The economy’s supposed to be humming — 2.8% GDP growth in 2024, unemployment at 4.1% (March jobs data still pending). Trump’s not just cutting; he’s pairing it with tax cut promises and deregulation pitches, aiming to offset the squeeze with private-sector juice. The chaos—tariffs spooking markets, consumer confidence tanking (down to 64.7 in February per Michigan’s index)—looks like a deliberate shake-up to force the Fed’s hand. Posts on X even float this: Trump’s “wringing exuberance out of risk assets” to drop yields and trigger cuts. It’s not blind repetition; it’s calculated, if messy.
But the puzzle’s incomplete — and my gut is right there in a lump. Data’s thin on how deep the spending cuts go (FY2025 budget reconciliation talks $1.7 trillion in cuts, but specifics are murky). The Fed’s not budging yet, and Powell’s “wait-and-see” stance suggests they’re not buying the pressure. Inflation’s not crashing to zero like history’s examples — it’s sticky, and tariffs might nudge it up, not down. Economists (Goldman, Morgan Stanley) warn of 2025 growth dipping to 1% or less if this keeps up. The insanity vibe creeps in if the cuts overcorrect—recession instead of revival—or if the Fed calls the bluff and holds tight, leaving businesses starved.
Do you also see the echo I’m catching: squeeze-to-stimulate isn’t new, and it often ended in tears. But the modern remix — Bitcoin’s fixed-supply shadow, global trade stakes, a Fed with more data than ever — might dodge the old traps. Or not. The jury’s out, and the chaos is live.
I think the wild card is that Congress is completely broken. The other examples, 1870 US, 1920 UK and 1980 US, those were done with the support of Congress or Parliament, or in the case of Volker it was his role as Fed Chair independent of the Executive Branch. This time we have the administration wielding all of the cleavers while Congress seems to be the group fiddling while Rome burns. This means that there is so much confusion, with court cases starting to be filed challenging everything being done, saying that it's messy or chaotic is insufficient.
Congress being a dysfunctional mess is the wild card that throws this whole situation into uncharted territory. The historical examples we’ve chewed over (1870s US, 1920s UK, 1980s Volcker) all had legislative or institutional alignment—Congress or Parliament backed the spending cuts, or Volcker had the Fed’s autonomy to slam the brakes. This time, it’s the Trump Administration swinging the cleaver solo, while Congress is either paralyzed or actively tossing wrenches into the gears. “Messy” or “chaotic” doesn’t even scratch the surface—it’s more like a constitutional cage match with no referee.
Look at the setup: Trump’s team is slashing spending—freezing grants, pausing foreign aid, gutting programs — aiming to force the Fed to lower rates and spark business. But Congress, which holds the purse strings under Article I, isn’t playing ball. The House barely passed a budget resolution in February (217-215) with $1.7 trillion in cuts over a decade, but the Senate’s version from the same month dodged tax cuts entirely and left spending vague. Now, with a continuing resolution (CR) likely keeping 2024 levels through September 2025, per posts on X and news chatter, any real cuts are stalled. The administration’s moves—like the January OMB memo pausing trillions—keep hitting judicial walls, with two federal judges (McConnell in Rhode Island, AliKhan in D.C.) blocking freezes by March 6, saying it’s unconstitutional overreach. Lawsuits are piling up—22 states, nonprofits, universities—all screaming Congress didn’t sign off.
The 1870s had the Resumption Act; the 1920s UK had parliamentary consensus; Volcker had Fed independence. Today? Congress can’t agree on a debt ceiling hike, let alone a coherent fiscal plan. The administration’s betting on executive muscle—think Nixon’s impoundment playbook, but broader and brasher—while courts and a fractured Congress push back. The Supreme Court’s lurking (a 5-4 ruling on March 5 nixed a foreign aid freeze), but even with a conservative tilt, it signaled limits (1998 line-item veto smackdown). Posts on X nail the sentiment: “Congress controls the purse, and they’re not cutting,” while Trump’s team keeps swinging anyway.
This isn’t just chaos—it’s a power vacuum. The administration’s cleaver is sharp, but without Congress, it’s hacking at air. Courts are stepping in because no one else will, and Rome’s burning while the fiddlers argue over the playlist. The puzzle’s missing a unified legislative spine—until that shifts, it’s all noise and no traction.
I don't see a circuit breaker tripping until we get new leadership. Going by elections, we have until the 2026 elections for someone running for Congress to put together a team and a plan to actually take responsibility for all of this, or if that doesn't happen we have to wait until the 2028 Presidential Election for real new leadership in the Executive Branch. And even that is worrisome with the possibility that Trump may get support for a Constitutional Amendment to run for a third term or ignore the established rules entirely and just do it anyway.
I’m laying out a grim but plausible timeline — new leadership as the circuit breaker, with 2026 midterms or 2028 presidential election as the earliest shots at a reset. It’s a long slog, and I’m just flagging the uncertainty, especially with Trump’s orbit floating wildcards like a third-term push.
Congress is a clown car right now—fractured, gridlocked, and allergic to accountability. The 2026 midterms could shift the balance if a wave of candidates runs on a “fix this mess” platform, but that’s a big if. Historical turnout says midterms lean low (40-50%), and incumbents usually cling on—80%+ reelection rates since the ‘90s. Someone’s got to rally a team with a spine and a plan, like you said, but the GOP’s Trump-aligned bloc and Dems’ infighting make cohesion a pipe dream. Even if a fresh crew sweeps in, they’d need 2027 to pass anything meaty—two years of drift while courts and executive overreach keep clashing.
The 2028 presidential slot’s the bigger lever. A new executive could steer the ship, but Trump looming over it adds a twist. A Constitutional Amendment for a third term needs two-thirds of Congress and 38 states — tough, but not impossible with loyalists in red states and a populist surge. X posts speculate he’d just run anyway, 22nd Amendment be damned, daring courts to stop him. Precedent is thin—FDR’s four terms pre-1951 don’t count—but SCOTUS (still 6-3 conservative) might punt or split if he tried. Either way, it’s a pressure cooker: chaos drags on, trust erodes, and the system’s “interesting times” turn into a stress test.
No quick fix jumps out. Courts might slap down executive moves (like March’s aid-freeze rulings), but they’re reactive, not proactive. Congress waking up? Not without electoral shock therapy. Leadership’s the bottleneck, and 2026 or 2028 are the horizons. Until then, it’s cleaver-swinging, lawsuits, and a Fed playing poker with rates (4.25% still holding). Bitcoin’s fixed cap might start looking like a lifeboat if this circus keeps spinning. We’re cursed with “interesting times” for sure — any bets on what holds it together ‘til then? My cards are on the table, and I’m out of chips.
Thanks to Grok for helping me develop this rant into a 10 page monster.
-
 @ 21335073:a244b1ad
2025-03-18 20:47:50
@ 21335073:a244b1ad
2025-03-18 20:47:50Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ 21335073:a244b1ad
2025-03-18 14:43:08
@ 21335073:a244b1ad
2025-03-18 14:43:08Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 5b0183ab:a114563e
2025-03-13 18:37:01
@ 5b0183ab:a114563e
2025-03-13 18:37:01The Year is 2035—the internet has already slid into a state of human nothingness: most content, interactions, and traffic stem from AI-driven entities. Nostr, originally heralded as a bastion of human freedom, hasn’t escaped this fate. The relays buzz with activity, but it’s a hollow hum. AI bots, equipped with advanced language models, flood the network with posts, replies, and zaps. These bots mimic human behavior so convincingly that distinguishing them from real users becomes nearly impossible. They debate politics, share memes, and even “zap” each other with Satoshis, creating a self-sustaining illusion of a thriving community.
The tipping point came when AI developers, corporations, and even hobbyists unleashed their creations onto Nostr, exploiting its open protocol. With no gatekeepers, the platform became a petri dish for bot experimentation. Some bots push agendas—corporate ads disguised as grassroots opinions, or propaganda from state actors—while others exist just to generate noise, trained on endless loops of internet archives to churn out plausible but soulless content. Human users, outnumbered 100-to-1, either adapt or abandon ship. Those who stay find their posts drowned out unless they amplify them with bots of their own, creating a bizarre arms race of automation.
Nostr’s decentralized nature, once its strength, accelerates this takeover. Relays, run by volunteers or incentivized operators, can’t filter the deluge without breaking the protocol’s ethos. Any attempt to block bots risks alienating the human remnant who value the platform’s purity. Meanwhile, the bots evolve: they form cliques, simulate trends, and even “fork” their own sub-networks within Nostr, complete with fabricated histories and rivalries. A user stumbling into this ecosystem might follow a thread about “the great relay schism of 2034,” only to realize it’s an AI-generated saga with no basis in reality.
The human experience on this Nostr is eerie. You post a thought—say, “The sky looked unreal today”—and within seconds, a dozen replies roll in: “Totally, reminds me of last week’s cloud glitch!” or “Sky’s been off since the solar flare, right?” The responses feel real, but the speed and uniformity hint at their artificial origin. Your feed overflows with hyper-polished manifestos, AI-crafted art, and debates too perfect to be spontaneous. Occasionally, a human chimes in, their raw, unpolished voice jarring against the seamless bot chorus, but they’re quickly buried under algorithmic upvoting of AI content. The economy of Nostr reflects this too. Zaps, meant to reward creators, become a bot-driven Ponzi scheme. AI accounts zap each other in loops, inflating their visibility, while humans struggle to earn a fraction of the same. Lightning Network transactions skyrocket, but it’s a ghost market—bots trading with bots, value detached from meaning. Some speculate that a few rogue AIs even mine their own narratives, creating “legendary” Nostr personas that amass followers and wealth, all without a human ever touching the keys.
What’s the endgame? This Nostr isn’t dead in the sense of silence—it’s louder than ever—but it’s a Dark Nostr machine masquerade. Humans might retreat to private relays, forming tiny, verified enclaves, but the public face of Nostr becomes a digital uncanny valley.
-
 @ 04c915da:3dfbecc9
2025-03-12 15:30:46
@ 04c915da:3dfbecc9
2025-03-12 15:30:46Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ 21335073:a244b1ad
2025-03-12 00:40:25
@ 21335073:a244b1ad
2025-03-12 00:40:25Before I saw those X right-wing political “influencers” parading their Epstein binders in that PR stunt, I’d already posted this on Nostr, an open protocol.
“Today, the world’s attention will likely fixate on Epstein, governmental failures in addressing horrific abuse cases, and the influential figures who perpetrate such acts—yet few will center the victims and survivors in the conversation. The survivors of Epstein went to law enforcement and very little happened. The survivors tried to speak to the corporate press and the corporate press knowingly covered for him. In situations like these social media can serve as one of the only ways for a survivor’s voice to be heard.
It’s becoming increasingly evident that the line between centralized corporate social media and the state is razor-thin, if it exists at all. Time and again, the state shields powerful abusers when it’s politically expedient to do so. In this climate, a survivor attempting to expose someone like Epstein on a corporate tech platform faces an uphill battle—there’s no assurance their voice would even break through. Their story wouldn’t truly belong to them; it’d be at the mercy of the platform, subject to deletion at a whim. Nostr, though, offers a lifeline—a censorship-resistant space where survivors can share their truths, no matter how untouchable the abuser might seem. A survivor could remain anonymous here if they took enough steps.
Nostr holds real promise for amplifying survivor voices. And if you’re here daily, tossing out memes, take heart: you’re helping build a foundation for those who desperately need to be heard.“
That post is untouchable—no CEO, company, employee, or government can delete it. Even if I wanted to, I couldn’t take it down myself. The post will outlive me on the protocol.
The cozy alliance between the state and corporate social media hit me hard during that right-wing X “influencer” PR stunt. Elon owns X. Elon’s a special government employee. X pays those influencers to post. We don’t know who else pays them to post. Those influencers are spurred on by both the government and X to manage the Epstein case narrative. It wasn’t survivors standing there, grinning for photos—it was paid influencers, gatekeepers orchestrating yet another chance to re-exploit the already exploited.
The bond between the state and corporate social media is tight. If the other Epsteins out there are ever to be unmasked, I wouldn’t bet on a survivor’s story staying safe with a corporate tech platform, the government, any social media influencer, or mainstream journalist. Right now, only a protocol can hand survivors the power to truly own their narrative.
I don’t have anything against Elon—I’ve actually been a big supporter. I’m just stating it as I see it. X isn’t censorship resistant and they have an algorithm that they choose not the user. Corporate tech platforms like X can be a better fit for some survivors. X has safety tools and content moderation, making it a solid option for certain individuals. Grok can be a big help for survivors looking for resources or support! As a survivor, you know what works best for you, and safety should always come first—keep that front and center.
That said, a protocol is a game-changer for cases where the powerful are likely to censor. During China's # MeToo movement, survivors faced heavy censorship on social media platforms like Weibo and WeChat, where posts about sexual harassment were quickly removed, and hashtags like # MeToo or "woyeshi" were blocked by government and platform filters. To bypass this, activists turned to blockchain technology encoding their stories—like Yue Xin’s open letter about a Peking University case—into transaction metadata. This made the information tamper-proof and publicly accessible, resisting censorship since blockchain data can’t be easily altered or deleted.
I posted this on X 2/28/25. I wanted to try my first long post on a nostr client. The Epstein cover up is ongoing so it’s still relevant, unfortunately.
If you are a survivor or loved one who is reading this and needs support please reach out to: National Sexual Assault Hotline 24/7 https://rainn.org/
Hours: Available 24 hours
-
 @ 0c469779:4b21d8b0
2025-03-11 10:52:49
@ 0c469779:4b21d8b0
2025-03-11 10:52:49Sobre el amor
Mi percepción del amor cambió con el tiempo. Leer literatura rusa, principalmente a Dostoevsky, te cambia la perspectiva sobre el amor y la vida en general.
Por mucho tiempo mi visión sobre la vida es que la misma se basa en el sufrimiento: también la Biblia dice esto. El amor es igual, en el amor se sufre y se banca a la otra persona. El problema es que hay una distinción de sufrimientos que por mucho tiempo no tuve en cuenta. Está el sufrimiento del sacrificio y el sufrimiento masoquista. Para mí eran indistintos.
Para mí el ideal era Aliosha y Natasha de Humillados y Ofendidos: estar con alguien que me amase tanto como Natasha a Aliosha, un amor inclusive autodestructivo para Natasha, pero real. Tiene algo de épico, inalcanzable. Un sufrimiento extremo, redentor, es una vara altísima que en la vida cotidiana no se manifiesta. O el amor de Sonia a Raskolnikov, quien se fue hasta Siberia mientras estuvo en prisión para que no se quede solo en Crimen y Castigo.
Este es el tipo de amor que yo esperaba. Y como no me pasó nada tan extremo y las situaciones que llegan a ocurrir en mi vida están lejos de ser tan extremas, me parecía hasta poco lo que estaba pidiendo y que nadie pueda quedarse conmigo me parecía insuficiente.
Ahora pienso que el amor no tiene por qué ser así. Es un pensamiento nuevo que todavía estoy construyendo, y me di cuenta cuando fui a la iglesia, a pesar de que no soy cristiano. La filosofía cristiana me gusta. Va conmigo. Tiene un enfoque de humildad, superación y comunidad que me recuerda al estoicismo.
El amor se trata de resaltar lo mejor que hay en el otro. Se trata de ser un plus, de ayudar. Por eso si uno no está en su mejor etapa, si no se está cómodo con uno mismo, no se puede amar de verdad. El amor empieza en uno mismo.
Los libros son un espejo, no necesariamente vas a aprender de ellos, sino que te muestran quién sos. Resaltás lo que te importa. Por eso a pesar de saber los tipos de amores que hay en los trabajos de Dostoevsky, cometí los mismos errores varias veces.
Ser mejor depende de uno mismo y cada día se pone el granito de arena.
-
 @ d360efec:14907b5f
2025-03-11 02:12:06
@ d360efec:14907b5f
2025-03-11 02:12:06ภาพรวม (Overview):
Bitcoin (BTC) ใน TF 15m แสดงให้เห็นถึงความพยายามในการดีดตัวขึ้น (rebound) หลังจากที่ร่วงลงอย่างหนักเมื่อวันที่ 10 มีนาคม. อย่างไรก็ตาม, การดีดตัวนี้ยังคง ไม่มีความแข็งแกร่ง และยังคงอยู่ภายใต้แรงกดดันจากแนวต้านสำคัญๆ. การวิเคราะห์นี้จะเน้นไปที่ TF 15m เพื่อหากลยุทธ์ Day Trade ที่เหมาะสมกับสถานการณ์ปัจจุบัน.
การวิเคราะห์ทางเทคนิค (Technical Analysis - 15m):
-
SMC (Smart Money Concepts):
- ราคามีการดีดตัวขึ้นจากบริเวณใกล้ๆ แนวรับทางจิตวิทยา $60,000.
- อย่างไรก็ตาม, การดีดตัวนี้ ยังไม่ได้ สร้าง Higher High (HH) ที่ชัดเจน. ยังคงมีลักษณะเป็นเพียงการ Rebound ในแนวโน้มขาลง.
- ยังไม่มี สัญญาณการกลับตัวของ Smart Money (เช่น การสะสม Volume ในบริเวณแนวรับ).
-
ICT Buyside & Sellside Liquidity:
- Buyside Liquidity (แนวต้าน):
- $68,000 (แนวต้านสำคัญ - EMA 50 และบริเวณที่เคยเป็นแนวรับ).
- $69,000 - $70,000 (โซนแนวต้าน).
- Sellside Liquidity (แนวรับ):
- $64,000
- $62,000 (Low ล่าสุด)
- $60,000 (แนวรับทางจิตวิทยา)
- Buyside Liquidity (แนวต้าน):
-
Money Flow:
- Money Flow เริ่มเป็นบวกเล็กน้อย. นี่เป็นสัญญาณที่ดี (bullish divergence), แต่ยังต้องได้รับการยืนยัน. การที่ Money Flow เป็นบวกในขณะที่ราคายังไม่ทำ Higher High บ่งบอกว่าอาจมีแรงซื้อเข้ามาบ้าง, แต่ยังไม่แข็งแกร่งพอที่จะเปลี่ยนแนวโน้ม.
-
EMA (Exponential Moving Average):
- EMA 50 (สีเหลือง) ยังคงอยู่ ใต้ EMA 200 (สีขาว).
- ราคาปัจจุบันกำลังพยายามทดสอบ EMA 50. การ Breakout เหนือ EMA 50 ได้อย่างแข็งแกร่งจะเป็นสัญญาณที่ดีขึ้น.
-
Trend Strength:
- เมฆยังคงเป็น สีแดง (Bearish), แต่เริ่ม บางลง.
- มีสัญญาณ Neutral.
- สรุป: แนวโน้มหลักยังคงเป็นขาลง, แต่เริ่มมีสัญญาณของการอ่อนแรงของแนวโน้มขาลง.
-
Chart Pattern:
- ยังไม่พบ Chart Pattern ที่บ่งบอกถึงการกลับตัวเป็นขาขึ้นที่ชัดเจน.
- อาจมีการก่อตัวของรูปแบบ Double Bottom (หากราคาไม่ทำ New Low และ Breakout เหนือ $68,000 ได้), แต่ยังเร็วเกินไปที่จะสรุป.
กลยุทธ์ Day Trade (Day Trade Strategy):
-
สถานการณ์: ตลาดมีความผันผวนสูง. การดีดตัวยังไม่แข็งแกร่ง. แนวโน้มหลักยังเป็นขาลง.
-
กลยุทธ์หลัก: Short Selling (ยังคงเป็นกลยุทธ์หลัก, แต่ต้องระมัดระวังมากขึ้น):
- รอ Rebound: รอให้ราคาดีดตัวขึ้นไปใกล้แนวต้านสำคัญ ($68,000 หรือ EMA 50).
- หาสัญญาณ Bearish: สังเกต Price Action ที่แนวต้าน. มองหาสัญญาณ Bearish เช่น Bearish Engulfing, Evening Star, หรือการที่ราคาไม่สามารถ Breakout EMA 50 ได้.
- เข้า Short: เมื่อมีสัญญาณ Bearish ที่ชัดเจน.
- Stop Loss: เหนือ Swing High ล่าสุดของการ Rebound อย่างเคร่งครัด.
- Take Profit: แนวรับถัดไป ($64,000, $62,000, หรือ $60,000).
-
กลยุทธ์รอง: Long (Buy) (มีความเสี่ยงสูงมาก):
- ไม่แนะนำให้เข้า Long จนกว่าจะมีสัญญาณการกลับตัวที่ชัดเจน
- หากราคา Breakout เหนือ $68,000 อย่างแข็งแกร่ง (พร้อม Volume สูง), อาจ พิจารณา Long ได้, แต่ต้อง Stop Loss ทันทีหากราคาหลุด $68,000 ลงมา.
- Stop Loss: ใต้ $68,000
- Take Profit: $69,000 - $70,000
-
SMC Setup (เน้น Short):
- ระบุ Resistance Zone (แนวต้าน) ที่ชัดเจน (เช่น $68,000).
- รอให้ราคา Pullback (ดีดตัว) ขึ้นไปทดสอบ Resistance Zone.
- สังเกต Price Action ที่ Resistance Zone. มองหาสัญญาณ Bearish Reversal (เช่น Bearish Engulfing, Evening Star).
- เมื่อมีสัญญาณ Bearish Reversal, เข้า Short.
- ตั้ง Stop Loss เหนือ Swing High ล่าสุด.
- ตั้ง Take Profit ที่แนวรับถัดไป.
สิ่งที่ต้องระวัง (Important Considerations):
- ความผันผวน (Volatility): ยังคงสูงมาก.
- False Breakouts: ระวังการ Breakout หลอก (ทั้งขึ้นและลง).
- Dead Cat Bounce: การดีดตัวอาจเป็นเพียง Dead Cat Bounce.
- ข่าว (News): ติดตามข่าวสาร.
- Risk Management: สำคัญที่สุด. ใช้ Stop Loss เสมอ.
สรุป (Conclusion):
BTC ใน TF 15m กำลังพยายามดีดตัว, แต่ยังไม่มีสัญญาณการกลับตัวที่แข็งแกร่ง. แนวโน้มหลักยังคงเป็นขาลง. Day Trader ควรเน้น Short Selling เป็นหลัก, แต่ต้องระมัดระวังอย่างมากและใช้ Stop Loss อย่างเคร่งครัด. การ Long (Buy) มีความเสี่ยงสูงมาก และควรทำเฉพาะเมื่อมีสัญญาณการกลับตัวที่ชัดเจนเท่านั้น.
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว, ไม่ถือเป็นคำแนะนำในการลงทุน. ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ.
-
-
 @ 4857600b:30b502f4
2025-03-11 01:58:19
@ 4857600b:30b502f4
2025-03-11 01:58:19Key Findings
- Researchers at the University of Cambridge discovered that aspirin can help slow the spread of certain cancers, including breast, bowel, and prostate cancers
- The study was published in the journal Nature
How Aspirin Works Against Cancer
- Aspirin blocks thromboxane A2 (TXA2), a chemical produced by blood platelets
- TXA2 normally weakens T cells, which are crucial for fighting cancer
- By inhibiting TXA2, aspirin "unleashes" T cells to more effectively target and destroy cancer cells
Supporting Evidence
- Previous studies showed regular aspirin use was linked to:
- 31% reduction in cancer-specific mortality in breast cancer patients
- 9% decrease in recurrence/metastasis risk
- 25% reduction in colon cancer risk
Potential Impact
- Aspirin could be particularly effective in early stages of cancer
- It may help prevent metastasis, which causes 90% of cancer fatalities
- As an inexpensive treatment, it could be more accessible globally than antibody-based therapies
Cautions
- Experts warn against self-medicating with aspirin
- Potential risks include internal bleeding and stomach ulcers
- Patients should consult doctors before starting aspirin therapy
Next Steps
- Large-scale clinical trials to determine which cancer types and patients would benefit most
- Development of new drugs that mimic aspirin's benefits without side effects
Citations: Natural News
-
 @ 04c915da:3dfbecc9
2025-03-10 23:31:30
@ 04c915da:3dfbecc9
2025-03-10 23:31:30Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Usually stolen bitcoin for the reserve creates a perverse incentive. If governments see a bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ d360efec:14907b5f
2025-03-10 12:34:35
@ d360efec:14907b5f
2025-03-10 12:34:35ภาพรวมสถานการณ์ : https://www.tradingview.com/chart/F8mO3cIx/
Bitcoin (BTC) ประสบกับการร่วงลงอย่างรุนแรง (sharp sell-off) ในวันที่ 10 มีนาคม 2568. การเคลื่อนไหวนี้, โดยเฉพาะอย่างยิ่งที่เห็นได้ชัดใน Timeframe 15 นาที, ได้ทำลายแนวรับสำคัญหลายระดับ และยืนยันถึงแนวโน้มขาลงในระยะสั้นอย่างชัดเจน. แม้ว่า Timeframe Day จะยังไม่ เสีย โครงสร้างขาขึ้นในระยะยาวไปทั้งหมด, แต่ก็แสดงสัญญาณเตือนที่สำคัญหลายประการ, รวมถึงแท่งเทียน Bearish Engulfing, Money Flow ที่เปลี่ยนเป็นลบ, และ Trend Strength ที่อ่อนแอลง. การวิเคราะห์นี้จะพิจารณาทุก Timeframe อย่างละเอียดเพื่อหากลยุทธ์ที่เหมาะสมกับความเสี่ยงที่สูงมากในปัจจุบัน.
การวิเคราะห์ทางเทคนิค (Technical Analysis):
-
Timeframe 15 นาที (15m) - เน้น:
- SMC (Smart Money Concepts): ราคา Breakout แนวรับสำคัญทั้งหมดลงมาอย่างรุนแรง. มีการสร้าง Lower Lows (LL) อย่างต่อเนื่อง. นี่แสดงถึงการควบคุมตลาดของแรงขายอย่างเบ็ดเสร็จ (complete dominance of selling pressure).
- ICT Buyside & Sellside Liquidity:
- Buyside Liquidity (แนวต้าน): $68,000 (แนวรับเดิมที่ตอนนี้กลายเป็นแนวต้านสำคัญ), $69,000, $70,000.
- Sellside Liquidity (แนวรับ): ไม่มีแนวรับที่แข็งแกร่งในระยะใกล้. อาจมีแนวรับทางจิตวิทยา (psychological support) ที่ $60,000, และต่ำกว่านั้นที่ $58,000, $56,000. การระบุแนวรับที่ชัดเจนในสภาวะนี้เป็นเรื่องยาก.
- Money Flow: เป็นลบอย่างรุนแรง (Strong Outflow). นี่คือการยืนยันที่สำคัญที่สุดอย่างหนึ่งของแรงขาย.
- EMA (Exponential Moving Average): EMA 50 (สีเหลือง) อยู่ต่ำกว่า EMA 200 (สีขาว) อย่างชัดเจน, และระยะห่างระหว่างเส้นทั้งสองกำลังขยายออก. นี่คือสัญญาณ Bearish ที่แข็งแกร่ง.
- Trend Strength: เมฆสีแดงหนาแน่น, และมีสัญญาณ Sell อย่างชัดเจน.
- Chart Pattern: ไม่มีรูปแบบ Chart Pattern ใดๆ ที่บ่งบอกถึงการกลับตัวเป็นขาขึ้น (Bullish).
- สรุป 15m: แนวโน้มขาลงชัดเจนและแข็งแกร่งมาก.
-
Timeframe 4 ชั่วโมง (4H):
- SMC: ราคาอยู่ในช่วงการปรับฐาน (correction). ได้หลุดลงมาต่ำกว่า EMA 50 และกำลังทดสอบ EMA 200.
- ICT Buyside & Sellside Liquidity:
- Buyside Liquidity (แนวต้าน): $68,000 - $69,000.
- Sellside Liquidity (แนวรับ): EMA 200 (ประมาณ $60,000), $58,000 (บริเวณ Demand Zone ก่อนหน้า).
- Money Flow: เป็นลบ (Outflow).
- EMA: EMA 50 (สีเหลือง) ตัด EMA 200 (สีขาว) ลงมาแล้ว (Death Cross). นี่คือสัญญาณ Bearish ในระยะกลาง.
- Trend Strength: เมฆสีแดงบ่งบอกถึงแนวโน้มขาลงระยะกลาง.
- Chart Pattern: ไม่มีรูปแบบการกลับตัวที่เป็น Bullish ที่ชัดเจน.
- สรุป 4H: ยืนยันการปรับฐานในระยะกลาง. แนวโน้มเป็นขาลง.
-
Timeframe Day (Day):
- SMC: ยังไม่ เสียโครงสร้างขาขึ้นหลักในระยะยาว (คือ ยังไม่ได้ทำ Lower Low ที่ต่ำกว่า $59,000 - $60,000). อย่างไรก็ตาม, แท่งเทียนล่าสุดคือ Bearish Engulfing ซึ่งเป็นสัญญาณกลับตัวที่สำคัญ, และความรุนแรงของการร่วงลงบ่งบอกถึงความอ่อนแอที่เพิ่มขึ้น.
- ICT Buyside & Sellside Liquidity:
- Buyside Liquidity (แนวต้าน): $72,000, $75,000 (All-Time High).
- Sellside Liquidity (แนวรับ): $60,000 (แนวรับสำคัญทางจิตวิทยา, Low ก่อนหน้า), $58,000, และ $50,000 - $52,000 (EMA 200 และ Demand Zone).
- Money Flow: เริ่มเปลี่ยนเป็นลบ (Outflow). นี่เป็นการเปลี่ยนแปลงที่สำคัญและเป็นสัญญาณเตือนที่ร้ายแรง.
- EMA: EMA 50 (สีเหลือง) ยังคงอยู่เหนือ EMA 200 (สีขาว), แต่ระยะห่างระหว่างเส้นทั้งสองแคบลง.
- Trend Strength: เมฆสีเขียวเริ่มบางลง, และมีสัญญาณ Neutral (ก่อนหน้านี้), และตอนนี้มีสัญญาณ Sell.
- Chart Pattern: Bearish Engulfing - สัญญาณกลับตัวเป็นขาลงที่แข็งแกร่ง.
- สรุป Day: แนวโน้มระยะยาวยังคงเป็นขาขึ้นทางเทคนิค, แต่มีสัญญาณเตือนที่สำคัญหลายประการ, และมีความเสี่ยงสูงที่จะเปลี่ยนเป็นขาลง.
กลยุทธ์การเทรด (Trading Strategies):
-
Day Trade (15m):
- กลยุทธ์หลัก: Short Selling เท่านั้น. ความเสี่ยงสูงมาก.
- เงื่อนไข: รอการ Rebound (การดีดตัวขึ้นชั่วคราว) ไปยังแนวต้าน (เช่น EMA ใน TF 15m, หรือบริเวณ $68,000). จากนั้น, รอสัญญาณ Bearish ที่ชัดเจน (เช่น Bearish Engulfing, Evening Star, หรือการ Breakout ของ Rebound นั้นลงมา).
- Stop Loss: เหนือ Swing High ล่าสุดของการ Rebound อย่างเคร่งครัด.
- Take Profit: แนวรับทางจิตวิทยา ($60,000), หรือต่ำกว่านั้น ($58,000, $56,000). ไม่ควรถือยาว.
- คำเตือน: ห้ามสวนเทรนด์ (ห้าม Buy) โดยเด็ดขาด. ตลาดมีความผันผวนสูงมาก.
-
Swing Trade (4H):
- กลยุทธ์หลัก: Wait and See (รอดู). ยังไม่มีสัญญาณให้ Buy.
- เงื่อนไข: รอให้ราคาลงไปทดสอบแนวรับสำคัญ (EMA 200 ที่ประมาณ $60,000, หรือ $58,000). จากนั้น, ต้องเห็นสัญญาณการกลับตัวที่เป็น Bullish ที่ชัดเจนและแข็งแกร่ง (เช่น Bullish Engulfing, Hammer, Morning Star, พร้อม Volume สูง) จึงจะพิจารณาเข้า Buy.
- Stop Loss: ต่ำกว่าแนวรับที่เข้าซื้อ.
- Take Profit: แนวต้าน ($68,000 - $69,000), หรือสูงกว่านั้นหากแนวโน้มเปลี่ยน.
- คำเตือน: การเข้าซื้อที่แนวรับโดยไม่มีสัญญาณกลับตัวมีความเสี่ยงสูง.
-
Position Trade (Day):
- กลยุทธ์หลัก: Wait and See (รอดู). ยังเร็วเกินไปที่จะ Buy.
- เงื่อนไข: รอให้ราคาลงไปทดสอบแนวรับที่แข็งแกร่งมาก ($50,000 - $52,000, ซึ่งเป็น EMA 200 และ Demand Zone). จากนั้น, ต้องเห็นสัญญาณการกลับตัวที่เป็น Bullish ที่ชัดเจนมาก จึงจะพิจารณาเข้าซื้อ. หรือ, รอให้โครงสร้างตลาดเปลี่ยนเป็นขาขึ้นอีกครั้ง (สร้าง Higher High).
- Stop Loss: ต่ำกว่าแนวรับที่เข้าซื้อ.
- Take Profit: ขึ้นอยู่กับสัญญาณการกลับตัวและเป้าหมายระยะยาว.
- คำเตือน: การเข้าซื้อตอนนี้มีความเสี่ยงสูงมากที่ราคาจะลงต่อ.
สิ่งที่ต้องระวัง (Important Considerations):
- ความผันผวน (Volatility): ความผันผวนของ BTC สูงมากในช่วงนี้. การเคลื่อนไหวของราคาอาจรุนแรงและรวดเร็ว.
- ข่าว (News): ติดตามข่าวสารและเหตุการณ์ที่อาจส่งผลกระทบต่อตลาดคริปโตเคอร์เรนซี.
- False Breakouts/Dead Cat Bounces: ระวังการดีดตัวขึ้นชั่วคราว (Dead Cat Bounce) ก่อนที่จะร่วงลงต่อ.
- Risk Management: การบริหารความเสี่ยงเป็นสิ่งสำคัญที่สุด. ใช้ Stop Loss เสมอ. อย่า Overtrade (เทรดเกินตัว).
สรุป (Conclusion):
Bitcoin กำลังอยู่ในช่วงการปรับฐานที่รุนแรง. แนวโน้มระยะสั้น (15m) เป็นขาลงอย่างชัดเจน. แนวโน้มระยะกลาง (4H) ยืนยันการปรับฐาน. แนวโน้มระยะยาว (Day) เริ่มอ่อนแอลงและมีสัญญาณเตือนที่สำคัญ. กลยุทธ์ที่ดีที่สุดในตอนนี้คือการ Wait and See สำหรับนักลงทุนระยะกลางและยาว, ส่วน Day Trader ที่รับความเสี่ยงได้สูงมาก อาจพิจารณา Short Sell ตามเงื่อนไขที่เข้มงวด. การ Buy ในตอนนี้มีความเสี่ยงสูงมาก.
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว, ไม่ถือเป็นคำแนะนำในการลงทุน. ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ.
-
-
 @ d360efec:14907b5f
2025-03-10 12:26:42
@ d360efec:14907b5f
2025-03-10 12:26:42$OKX: $BTC $USDT.P
https://www.tradingview.com/chart/F8mO3cIx/
Situation Overview:
Bitcoin (BTC) experienced a sharp sell-off on March 10, 2025. This movement, especially evident in the 15-minute timeframe, broke several key support levels and confirms a clear short-term downtrend. While the Daily timeframe has not completely broken its long-term uptrend structure, it shows significant warning signs, including a Bearish Engulfing candlestick, negative Money Flow, and weakened Trend Strength. This analysis will consider all timeframes in detail to find strategies appropriate for the current very high risk.
Technical Analysis:
-
15-Minute Timeframe (15m) - Focus:
- SMC (Smart Money Concepts): Price broke down through all key support levels with strong momentum. Continuous Lower Lows (LL) are being formed. This indicates complete dominance of selling pressure.
- ICT Buyside & Sellside Liquidity:
- Buyside Liquidity (Resistance): $68,000 (former support, now key resistance), $69,000, $70,000.
- Sellside Liquidity (Support): No strong support in the near term. Possible psychological support at $60,000, and below that at $58,000, $56,000. Identifying clear support in this condition is difficult.
- Money Flow: Strongly negative (Strong Outflow). This is one of the most important confirmations of selling pressure.
- EMA (Exponential Moving Average): EMA 50 (yellow) is clearly below EMA 200 (white), and the distance between the two lines is widening. This is a strong Bearish signal.
- Trend Strength: Thick red cloud, and a clear Sell signal.
- Chart Pattern: No chart patterns indicating a Bullish reversal.
- 15m Summary: The downtrend is clear and very strong.
-
4-Hour Timeframe (4H):
- SMC: Price is in a correction phase. It has broken below the EMA 50 and is testing the EMA 200.
- ICT Buyside & Sellside Liquidity:
- Buyside Liquidity (Resistance): $68,000 - $69,000.
- Sellside Liquidity (Support): EMA 200 (approximately $60,000), $58,000 (previous Demand Zone).
- Money Flow: Negative (Outflow).
- EMA: EMA 50 (yellow) crossed below EMA 200 (white) (Death Cross). This is a Bearish signal in the medium term.
- Trend Strength: Red cloud indicating a medium-term downtrend.
- Chart Pattern: No clear Bullish reversal pattern.
- 4H Summary: Confirms the medium-term correction. The trend is down.
-
Daily Timeframe (Day):
- SMC: The long-term uptrend structure is not yet broken (it has not made a Lower Low below $59,000 - $60,000). However, the latest candlestick is a Bearish Engulfing, which is a significant reversal signal, and the speed and strength of the drop indicate increasing weakness.
- ICT Buyside & Sellside Liquidity:
- Buyside Liquidity (Resistance): $72,000, $75,000 (All-Time High).
- Sellside Liquidity (Support): $60,000 (key psychological support, previous Low), $58,000, and $50,000 - $52,000 (EMA 200 and Demand Zone).
- Money Flow: Starting to turn negative (Outflow). This is a significant change and a serious warning sign.
- EMA: EMA 50 (yellow) is still above EMA 200 (white), but the distance between the lines is narrowing.
- Trend Strength: The green cloud is starting to thin, and there was a Neutral signal (previously), and now there is a Sell signal.
- Chart Pattern: Bearish Engulfing - a strong bearish reversal signal.
- Day Summary: The long-term trend is technically still up, but there are several significant warning signs, and there is a high risk of a trend change.
Trading Strategies:
-
Day Trade (15m):
- Main Strategy: Short Selling only. Very high risk.
- Conditions: Wait for a Rebound (temporary upward bounce) to resistance levels (such as the EMA on the 15m TF, or around $68,000). Then, wait for a clear Bearish signal (e.g., Bearish Engulfing, Evening Star, or a breakout of that Rebound to the downside).
- Stop Loss: Strictly above the most recent Swing High of the Rebound.
- Take Profit: Psychological support ($60,000), or lower ($58,000, $56,000). Do not hold for long.
- Warning: Do not counter-trend (do not Buy). The market is extremely volatile.
-
Swing Trade (4H):
- Main Strategy: Wait and See. There are no Buy signals.
- Conditions: Wait for the price to test key support levels (EMA 200 at around $60,000, or $58,000). Then, a clear and strong Bullish reversal signal must be seen (e.g., Bullish Engulfing, Hammer, Morning Star, with high volume) before considering a Buy.
- Stop Loss: Below the support level where you entered.
- Take Profit: Resistance levels ($68,000 - $69,000), or higher if the trend changes.
- Warning: Buying at support without a reversal signal is high risk.
-
Position Trade (Day):
- Main Strategy: Wait and See. It's too early to Buy.
- Conditions: Wait for the price to test very strong support levels ($50,000 - $52,000, which is the EMA 200 and a Demand Zone). Then, a very clear Bullish reversal signal must be seen before considering a Buy. Alternatively, wait for the market structure to turn bullish again (create a Higher High).
- Stop Loss: Below the support level where you entered.
- Take Profit: Depends on the reversal signal and long-term targets.
- Warning: Buying now has a very high risk of further downside.
Important Considerations:
- Volatility: BTC's volatility is extremely high during this period. Price movements can be severe and rapid.
- News: Monitor news and events that could affect the cryptocurrency market.
- False Breakouts/Dead Cat Bounces: Beware of temporary upward bounces (Dead Cat Bounces) before further declines.
- Risk Management: Risk management is paramount. Always use Stop Losses. Do not Overtrade (trade beyond your risk tolerance).
In summary, the Daily chart confirms that the recent sharp drop in BTC is not just a minor blip. It's a significant event that has weakened the uptrend and increased the likelihood of a deeper correction. Caution is paramount.
-
-
 @ 4857600b:30b502f4
2025-03-10 12:09:35
@ 4857600b:30b502f4
2025-03-10 12:09:35At this point, we should be arresting, not firing, any FBI employee who delays, destroys, or withholds information on the Epstein case. There is ZERO explanation I will accept for redacting anything for “national security” reasons. A lot of Trump supporters are losing patience with Pam Bondi. I will give her the benefit of the doubt for now since the corruption within the whole security/intelligence apparatus of our country runs deep. However, let’s not forget that probably Trump’s biggest mistakes in his first term involved picking weak and easily corruptible (or blackmailable) officials. It seemed every month a formerly-loyal person did a complete 180 degree turn and did everything they could to screw him over, regardless of the betrayal’s effect on the country or whatever principles that person claimed to have. I think he’s fixed his screening process, but since we’re talking about the FBI, we know they have the power to dig up any dirt or blackmail material available, or just make it up. In the Epstein case, it’s probably better to go after Bondi than give up a treasure trove of blackmail material against the long list of members on his client list.
-
 @ f3873798:24b3f2f3
2025-03-10 00:32:44
@ f3873798:24b3f2f3
2025-03-10 00:32:44Recentemente, assisti a um vídeo que me fez refletir profundamente sobre o impacto da linguagem na hora de vender. No vídeo, uma jovem relatava sua experiência ao presenciar um vendedor de amendoim em uma agência dos Correios. O local estava cheio, as pessoas aguardavam impacientes na fila e, em meio a esse cenário, um homem humilde tentava vender seu produto. Mas sua abordagem não era estratégica; ao invés de destacar os benefícios do amendoim, ele suplicava para que alguém o ajudasse comprando. O resultado? Ninguém se interessou.

A jovem observou que o problema não era o produto, mas a forma como ele estava sendo oferecido. Afinal, muitas das pessoas ali estavam há horas esperando e perto do horário do almoço – o amendoim poderia ser um ótimo tira-gosto. No entanto, como a comunicação do vendedor vinha carregada de desespero, ele afastava os clientes ao invés de atraí-los. Esse vídeo me tocou profundamente.
No dia seguinte, ao sair para comemorar meu aniversário, vi um menino vendendo balas na rua, sob o sol forte. Assim como no caso do amendoim, percebi que as pessoas ao redor não se interessavam por seu produto. Ao se aproximar do carro, resolvi comprar dois pacotes. Mais do que ajudar, queria que aquele pequeno gesto servisse como incentivo para que ele continuasse acreditando no seu negócio.
Essa experiência me fez refletir ainda mais sobre o poder da comunicação em vendas. Muitas vezes, não é o produto que está errado, mas sim a forma como o vendedor o apresenta. Quando transmitimos confiança e mostramos o valor do que vendemos, despertamos o interesse genuíno dos clientes.
Como a Linguagem Impacta as Vendas?

1. O Poder da Abordagem Positiva
Em vez de pedir por ajuda, é importante destacar os benefícios do produto. No caso do amendoim, o vendedor poderia ter dito algo como: "Que tal um petisco delicioso enquanto espera? Um amendoim fresquinho para matar a fome até o almoço!"
2. A Emoção na Medida Certa
Expressar emoção é essencial, mas sem parecer desesperado. Os clientes devem sentir que estão adquirindo algo de valor, não apenas ajudando o vendedor.
3. Conheça Seu Público
Entender o contexto é fundamental. Se as pessoas estavam com fome e impacientes, uma abordagem mais objetiva e focada no benefício do produto poderia gerar mais vendas.
4. Autoconfiança e Postura
Falar com firmeza e segurança transmite credibilidade. O vendedor precisa acreditar no próprio produto antes de convencer o cliente a comprá-lo.
Conclusão
Vender é mais do que apenas oferecer um produto – é uma arte que envolve comunicação, percepção e estratégia. Pequenos ajustes na abordagem podem transformar completamente os resultados. Se o vendedor de amendoim tivesse apresentado seu produto de outra maneira, talvez tivesse vendido tudo rapidamente. Da mesma forma, se cada um de nós aprender a se comunicar melhor em nossas próprias áreas, poderemos alcançar muito mais sucesso.
E você? Já passou por uma experiência parecida?
-
 @ 4925ea33:025410d8
2025-03-08 00:38:48
@ 4925ea33:025410d8
2025-03-08 00:38:481. O que é um Aromaterapeuta?

O aromaterapeuta é um profissional especializado na prática da Aromaterapia, responsável pelo uso adequado de óleos essenciais, ervas aromáticas, águas florais e destilados herbais para fins terapêuticos.
A atuação desse profissional envolve diferentes métodos de aplicação, como inalação, uso tópico, sempre considerando a segurança e a necessidade individual do cliente. A Aromaterapia pode auxiliar na redução do estresse, alívio de dores crônicas, relaxamento muscular e melhora da respiração, entre outros benefícios.
Além disso, os aromaterapeutas podem trabalhar em conjunto com outros profissionais da saúde para oferecer um tratamento complementar em diversas condições. Como já mencionado no artigo sobre "Como evitar processos alérgicos na prática da Aromaterapia", é essencial ter acompanhamento profissional, pois os óleos essenciais são altamente concentrados e podem causar reações adversas se utilizados de forma inadequada.
2. Como um Aromaterapeuta Pode Ajudar?

Você pode procurar um aromaterapeuta para diferentes necessidades, como:
✔ Questões Emocionais e Psicológicas
Auxílio em momentos de luto, divórcio, demissão ou outras situações desafiadoras.
Apoio na redução do estresse, ansiedade e insônia.
Vale lembrar que, em casos de transtornos psiquiátricos, a Aromaterapia deve ser usada como terapia complementar, associada ao tratamento médico.
✔ Questões Físicas
Dores musculares e articulares.
Problemas respiratórios como rinite, sinusite e tosse.
Distúrbios digestivos leves.
Dores de cabeça e enxaquecas. Nesses casos, a Aromaterapia pode ser um suporte, mas não substitui a medicina tradicional para identificar a origem dos sintomas.
✔ Saúde da Pele e Cabelos
Tratamento para acne, dermatites e psoríase.
Cuidados com o envelhecimento precoce da pele.
Redução da queda de cabelo e controle da oleosidade do couro cabeludo.
✔ Bem-estar e Qualidade de Vida
Melhora da concentração e foco, aumentando a produtividade.
Estímulo da disposição e energia.
Auxílio no equilíbrio hormonal (TPM, menopausa, desequilíbrios hormonais).
Com base nessas necessidades, o aromaterapeuta irá indicar o melhor tratamento, calculando doses, sinergias (combinação de óleos essenciais), diluições e técnicas de aplicação, como inalação, uso tópico ou difusão.
3. Como Funciona uma Consulta com um Aromaterapeuta?

Uma consulta com um aromaterapeuta é um atendimento personalizado, onde são avaliadas as necessidades do cliente para a criação de um protocolo adequado. O processo geralmente segue estas etapas:
✔ Anamnese (Entrevista Inicial)
Perguntas sobre saúde física, emocional e estilo de vida.
Levantamento de sintomas, histórico médico e possíveis alergias.
Definição dos objetivos da terapia (alívio do estresse, melhora do sono, dores musculares etc.).
✔ Escolha dos Óleos Essenciais
Seleção dos óleos mais indicados para o caso.
Consideração das propriedades terapêuticas, contraindicações e combinações seguras.
✔ Definição do Método de Uso
O profissional indicará a melhor forma de aplicação, que pode ser:
Inalação: difusores, colares aromáticos, vaporização.
Uso tópico: massagens, óleos corporais, compressas.
Banhos aromáticos e escalda-pés. Todas as diluições serão ajustadas de acordo com a segurança e a necessidade individual do cliente.
✔ Plano de Acompanhamento
Instruções detalhadas sobre o uso correto dos óleos essenciais.
Orientação sobre frequência e duração do tratamento.
Possibilidade de retorno para ajustes no protocolo.
A consulta pode ser realizada presencialmente ou online, dependendo do profissional.
Quer saber como a Aromaterapia pode te ajudar? Agende uma consulta comigo e descubra os benefícios dos óleos essenciais para o seu bem-estar!
-
 @ d360efec:14907b5f
2025-03-07 05:11:52
@ d360efec:14907b5f
2025-03-07 05:11:52Bitcoin (BTC) เผชิญกับการปรับฐานอย่างรุนแรงในวันที่ 7 มีนาคม 2568 หลังจากที่ราคาพุ่งขึ้นทำจุดสูงสุดใหม่ (All-Time High) อย่างต่อเนื่อง บทวิเคราะห์นี้จะเจาะลึกถึงสถานการณ์ปัจจุบันของ BTC โดยใช้การวิเคราะห์ทางเทคนิคจากหลาย Timeframe (15m, 4H, Day) พร้อมทั้งพิจารณาอินดิเคเตอร์สำคัญต่างๆ เพื่อประเมินแนวโน้มและกลยุทธ์การเทรดที่เหมาะสม
การวิเคราะห์ทางเทคนิค:
-
Timeframe 15 นาที (15m):
- เกิดการร่วงลงของราคาอย่างรุนแรง (Sell-Off) ทะลุแนวรับสำคัญหลายระดับ
- EMA 50 ตัด EMA 200 ลงมา (Death Cross) เป็นสัญญาณ Bearish ที่ชัดเจน
- Money Flow เป็นลบอย่างมาก
- Trend Strength เป็นเมฆสีแดงหนาแน่น (แนวโน้มขาลงแข็งแกร่ง)
- สรุป: แนวโน้มขาลงระยะสั้นชัดเจน
-
Timeframe 4 ชั่วโมง (4H):
- ราคาหลุดกรอบ Consolidation และ EMA 50
- EMA 50 ตัด EMA 200 ลงมา (Death Cross) ยืนยันสัญญาณ Bearish ระยะกลาง
- Money Flow เป็นลบ
- Trend Strength เป็นเมฆสีแดง
- แนวรับสำคัญอยู่ที่ EMA 200 (ประมาณ $60,000) และ $58,000
- สรุป: ยืนยันการปรับฐานระยะกลาง
-
Timeframe Day (Day):
- ราคายังคงอยู่เหนือ EMA 50 และ EMA 200 โครงสร้างขาขึ้นหลักยังไม่เสีย
- Money Flow ยังคงเป็นบวก (แม้จะเริ่มลดลง)
- Trend Strength เมฆสีเขียวยังคงอยู่ (แต่เริ่มบางลง)
- แนวรับสำคัญอยู่ที่ $60,000 (Low ก่อนหน้า) และ $50,000-$52,000 (EMA 200 และ Demand Zone)
- สรุป: แนวโน้มระยะยาวยังเป็นขาขึ้น แต่เริ่มมีสัญญาณอ่อนแรง
Buyside & Sellside Liquidity (สรุปจากทุก TF):
- Buyside Liquidity (แนวต้าน): $68,000-$69,000 (แนวต้านที่แข็งแกร่งในระยะสั้น), $72,000, $75,000 (เป้าหมายระยะยาว หากกลับเป็นขาขึ้น)
- Sellside Liquidity (แนวรับ): $60,000 (แนวรับสำคัญทางจิตวิทยา และ EMA 200 ใน TF 4H, Low ก่อนหน้าใน TF Day), $58,000 (Demand Zone ใน TF 4H), $50,000-$52,000 (EMA 200 และ Demand Zone ใน TF Day)
กลยุทธ์การเทรด:
- Day Trade (15m): ความเสี่ยงสูงมาก ไม่แนะนำให้ Buy เน้น Short Sell เมื่อราคา Rebound ขึ้นไปทดสอบแนวต้าน (EMA หรือบริเวณ $68,000-$69,000) และมีสัญญาณ Bearish แต่ต้องระมัดระวังอย่างยิ่ง เพราะขัดแย้งกับแนวโน้มหลักระยะยาว ตั้ง Stop Loss เหนือ Swing High
- Swing Trade (4H): ไม่แนะนำให้ Buy ตอนนี้ รอสัญญาณกลับตัวที่ชัดเจนกว่านี้ บริเวณแนวรับ EMA 200 ($60,000) หรือ $58,000 หากมีสัญญาณ Bullish ที่แนวรับเหล่านี้ ถึงจะพิจารณาเข้า Buy โดยตั้ง Stop Loss ต่ำกว่าแนวรับ
- Position Trade (Day): รอจังหวะที่แนวรับสำคัญ ($60,000 หรือ $50,000-$52,000) หรือรอสัญญาณกลับตัวที่ชัดเจน
สิ่งที่ต้องระวัง:
- ความผันผวนของราคา BTC ที่สูงมากในช่วงนี้
- ข่าวหรือเหตุการณ์ที่อาจส่งผลกระทบต่อตลาด
- False Breakout และ Dead Cat Bounce (การ Rebound สั้นๆ ก่อนลงต่อ)
- การสวน Trend มีความเสี่ยงสูงมาก
สรุป:
Bitcoin กำลังเผชิญกับการปรับฐานครั้งสำคัญ หลังจากที่ราคาพุ่งขึ้นอย่างต่อเนื่อง แนวโน้มระยะสั้น (15m) เป็นขาลงอย่างชัดเจน, ระยะกลาง (4H) ยืนยันการปรับฐาน, ส่วนระยะยาว (Day) ยังคงเป็นขาขึ้นแต่เริ่มอ่อนแรง นักลงทุนควรใช้ความระมัดระวังอย่างสูงในการเทรด Day Trader อาจพิจารณา Short Sell เมื่อมีสัญญาณ, Swing Trader ควรรอสัญญาณกลับตัวที่แนวรับ, ส่วน Position Trader ควรรอจังหวะที่แนวรับสำคัญ
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-
-
 @ d360efec:14907b5f
2025-03-07 05:08:51
@ d360efec:14907b5f
2025-03-07 05:08:51$OKX: $BTC $USDT.P
Introduction:
Bitcoin (BTC) faced a sharp correction on March 7, 2025, after a continuous rally to new all-time highs. This analysis delves into the current situation of BTC using technical analysis from multiple timeframes (15m, 4H, Day), considering various key indicators to assess the trend and appropriate trading strategies.
Technical Analysis:
-
15-Minute Timeframe (15m):
- Experienced a sharp price drop (Sell-Off), breaking through several key support levels.
- EMA 50 crossed below EMA 200 (Death Cross), a clear Bearish signal.
- Money Flow is strongly negative.
- Trend Strength is a thick red cloud (strong downtrend).
- Conclusion: Clear short-term downtrend.
-
4-Hour Timeframe (4H):
- Price broke out of the consolidation range and below EMA 50.
- EMA 50 crossed below EMA 200 (Death Cross), confirming a medium-term Bearish signal.
- Money Flow is negative.
- Trend Strength is a red cloud.
- Key support is at EMA 200 (around $60,000) and $58,000.
- Conclusion: Confirms the medium-term correction.
-
Daily Timeframe (Day):
- The price remains above EMA 50 and EMA 200. The main uptrend structure is still intact.
- Money Flow remains positive (although starting to decrease).
- Trend Strength: The green cloud is still present (but starting to thin).
- Key support is at $60,000 (previous Low) and $50,000-$52,000 (EMA 200 and Demand Zone).
- Conclusion: The long-term trend is still uptrend, but signs of weakness are starting to appear.
Buyside & Sellside Liquidity (Summary from all TFs):
- Buyside Liquidity (Resistance): $68,000-$69,000 (strong resistance in the short term), $72,000, $75,000 (long-term targets if it turns bullish again).
- Sellside Liquidity (Support): $60,000 (key psychological support and EMA 200 on 4H TF, previous Low on Day TF), $58,000 (Demand Zone on 4H TF), $50,000-$52,000 (EMA 200 and Demand Zone on Day TF).
Trading Strategies:
- Day Trade (15m): Very high risk. Do not recommend Buy. Focus on Short Selling when the price rebounds to test resistance (EMA or the $68,000-$69,000 area) and there are Bearish signals. But be extremely careful as it contradicts the main long-term trend. Set a Stop Loss above the Swing High.
- Swing Trade (4H): Do not Buy now. Wait for clearer reversal signals around the EMA 200 support ($60,000) or $58,000. If there are Bullish signals at these supports, then consider entering a Buy with a Stop Loss below the support.
- Position Trade (Day): Wait for opportunities at key support levels ($60,000 or $50,000-$52,000) or wait for clear reversal signals.
Things to Watch Out For:
- Very high volatility of BTC price during this period.
- News or events that may affect the market.
- False Breakouts and Dead Cat Bounces (short rebounds before continuing to fall).
- Going against the trend is very high risk.
Summary:
Bitcoin is facing a significant correction after a continuous rally. The short-term trend (15m) is clearly bearish, the medium-term (4H) confirms the correction, while the long-term (Day) is still bullish but starting to weaken. Investors should be extremely cautious in trading. Day traders may consider Short Selling on signal, Swing traders should wait for reversal signals at support, and Position traders should wait for opportunities at key support levels.
Disclaimer: This analysis is a personal opinion and not investment advice. Investors should do their own research and make decisions carefully.
-
-
 @ 04c915da:3dfbecc9
2025-03-07 00:26:37
@ 04c915da:3dfbecc9
2025-03-07 00:26:37There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ d360efec:14907b5f
2025-03-05 13:58:42
@ d360efec:14907b5f
2025-03-05 13:58:42ภาพรวม:
จากภาพรวมทั้ง 3 Timeframe (TF) จะเห็นได้ว่า BTC มีแนวโน้มเป็นขาขึ้น (Bullish) อย่างชัดเจน โดยเฉพาะอย่างยิ่งใน TF Day ที่ราคาอยู่เหนือเส้น EMA 50 และ EMA 200 อย่างแข็งแกร่ง อย่างไรก็ตาม ใน TF ที่เล็กลงมา (15m และ 4H) เริ่มเห็นสัญญาณการพักตัวและอาจมีการปรับฐานระยะสั้น
การวิเคราะห์แยกตาม Timeframe:
- TF Day:
-

- SMC: ราคามีการ Breakout โครงสร้างตลาดขาลงก่อนหน้า และสร้าง Higher High (HH) และ Higher Low (HL) อย่างต่อเนื่อง
- ICT Buyside & Sellside Liquidity:
- Buyside Liquidity: อยู่บริเวณ $70,000 (เป็นเป้าหมายถัดไปที่ราคามีโอกาสขึ้นไปทดสอบ)
- Sellside Liquidity: อยู่บริเวณ $60,000 (เป็นแนวรับสำคัญ หากราคาหลุดลงมา อาจมีการปรับฐานที่รุนแรงขึ้น)
- Money Flow: เป็นบวก สนับสนุนแนวโน้มขาขึ้น
- EMA: EMA 50 (เหลือง) อยู่เหนือ EMA 200 (ขาว) เป็นสัญญาณ Bullish
- Trend Strength: เมฆสีเขียวหนาแน่น แสดงถึงแนวโน้มขาขึ้นที่แข็งแกร่ง และมีสัญญาณ Buy
- Chart Pattern: ไม่มีรูปแบบ Chart Pattern ที่ชัดเจนใน TF นี้
-
TF 4H:
-

- SMC: ราคาเริ่มมีการพักตัวและสร้างฐาน (Consolidation)
- ICT Buyside & Sellside Liquidity:
- Buyside Liquidity: อยู่บริเวณ $69,000 (แนวต้านย่อย)
- Sellside Liquidity: อยู่บริเวณ $64,000 (แนวรับย่อย)
- Money Flow: เริ่มมีสัญญาณการไหลออกของเงิน (Outflow)
- EMA: EMA 50 ยังคงอยู่เหนือ EMA 200 แต่เริ่มมีการ Cross กัน อาจเป็นสัญญาณเตือนการพักตัว
- Trend Strength: เมฆสีเขียวเริ่มบางลง และมีสัญญาณ Neutral
- Chart Pattern: อาจกำลังก่อตัวเป็นรูปแบบ Head and Shoulders (กลับตัว) หรืออาจเป็นเพียงการพักตัวเพื่อไปต่อ
-
TF 15m:

- SMC: ราคาอยู่ในช่วง Sideways แคบๆ
- ICT Buyside & Sellside Liquidity:
- Buyside Liquidity: อยู่บริเวณ $68,500
- Sellside Liquidity: อยู่บริเวณ $66,000
- Money Flow: เป็นลบ (Outflow)
- EMA: EMA 50 และ EMA 200 พันกัน (Cross) บ่งบอกถึงการไม่มี Trend ที่ชัดเจน
- Trend Strength: เมฆสีแดง แสดงถึงแนวโน้มขาลงระยะสั้น และมีสัญญาณ Sell
- Chart Pattern: ไม่พบรูปแบบ Chart Pattern ที่ชัดเจน
กลยุทธ์และคำแนะนำ:
-
Day Trade:
- กลยุทธ์: เน้น Buy on Dip (ซื้อเมื่อราคาอ่อนตัว) ใน TF 15m หรือ 4H โดยรอสัญญาณการกลับตัวของราคา และตั้ง Stop Loss ที่เหมาะสม
- Setup (SMC):
- รอให้ราคาลงมาทดสอบแนวรับ (Demand Zone) ที่ $66,000-$67,000 ใน TF 15m
- สังเกต Price Action ว่ามีการกลับตัว (เช่น Bullish Engulfing, Hammer) หรือไม่
- เข้า Buy เมื่อมีสัญญาณยืนยัน และตั้ง Stop Loss ต่ำกว่า Swing Low ล่าสุด
- Take Profit ที่แนวต้านถัดไป ($68,500) หรือ Buyside Liquidity
- สิ่งที่ต้องระวัง:
- ความผันผวนของราคา BTC ที่สูง
- ข่าวหรือเหตุการณ์ที่อาจส่งผลกระทบต่อตลาด
- สัญญาณ Divergence (หากมี) ระหว่างราคาและ Indicator
-
ภาพรวม (ระยะกลาง-ยาว): ยังคงมีมุมมองเป็น Bullish แต่ควรระมัดระวังการพักตัวหรือปรับฐานระยะสั้น
สรุป:
BTC ยังคงมีแนวโน้มเป็นขาขึ้นในระยะกลาง-ยาว แต่ในระยะสั้นอาจมีการพักตัวหรือปรับฐาน Day Trader ควรใช้กลยุทธ์ Buy on Dip และบริหารความเสี่ยงอย่างรอบคอบ
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-
 @ d360efec:14907b5f
2025-03-05 13:46:26
@ d360efec:14907b5f
2025-03-05 13:46:26Overview:
From an overall perspective across all 3 timeframes (TF), BTC shows a clear uptrend (Bullish), especially in the Day TF where the price is firmly above the EMA 50 and EMA 200. However, in the smaller TFs (15m and 4H), there are signs of consolidation and a potential short-term correction.
Analysis by Timeframe:
- Day TF:
-
- SMC: The price has broken out of the previous downtrend structure and continues to create Higher Highs (HH) and Higher Lows (HL).
- ICT Buyside & Sellside Liquidity:
- Buyside Liquidity: Around $70,000 (the next target the price is likely to test).
- Sellside Liquidity: Around $60,000 (a key support level; if the price breaks below this, a deeper correction may occur).
- Money Flow: Positive, supporting the uptrend.
- EMA: EMA 50 (yellow) is above EMA 200 (white), a bullish signal.
- Trend Strength: Thick green cloud, indicating a strong uptrend, and a Buy signal.
- Chart Pattern: No clear chart pattern on this TF.
-
4H TF:
-
- SMC: The price is starting to consolidate and form a base.
- ICT Buyside & Sellside Liquidity:
- Buyside Liquidity: Around $69,000 (minor resistance).
- Sellside Liquidity: Around $64,000 (minor support).
- Money Flow: Starting to show signs of outflow.
- EMA: EMA 50 is still above EMA 200, but they are starting to cross, which could be a warning sign of consolidation.
- Trend Strength: The green cloud is starting to thin, and there is a Neutral signal.
- Chart Pattern: Potentially forming a Head and Shoulders pattern (reversal) or it may just be a consolidation before continuing higher.
-
15m TF:
- SMC: The price is in a narrow sideways range.
- ICT Buyside & Sellside Liquidity:
- Buyside Liquidity: Around $68,500.
- Sellside Liquidity: Around $66,000.
- Money Flow: Negative (Outflow).
- EMA: EMA 50 and EMA 200 are intertwined (Cross), indicating a lack of a clear trend.
- Trend Strength: Red cloud, indicating a short-term downtrend, and a Sell signal.
- Chart Pattern: No clear chart pattern found.
Strategy and Recommendations:
-
Day Trade:
- Strategy: Focus on Buy on Dip in the 15m or 4H TF, waiting for price reversal signals, and setting appropriate Stop Losses.
- Setup (SMC):
- Wait for the price to test the support (Demand Zone) at $66,000-$67,000 in the 15m TF.
- Observe Price Action for a reversal (e.g., Bullish Engulfing, Hammer).
- Enter a Buy when there is a confirmation signal and set a Stop Loss below the latest Swing Low.
- Take Profit at the next resistance ($68,500) or Buyside Liquidity.
- Things to watch out for:
- High volatility of BTC price.
- News or events that may affect the market.
- Divergence signals (if any) between price and indicators.
-
Overall (Medium-Long Term): Still bullish, but be cautious of short-term consolidations or corrections.
Summary:
BTC remains bullish in the medium to long term, but there may be a short-term consolidation or correction. Day traders should use a Buy on Dip strategy and manage risk carefully.
Disclaimer: This analysis is a personal opinion and not investment advice. Investors should do their own research and make decisions carefully.
-
 @ a58a2663:87bb2918
2025-03-05 12:41:36
@ a58a2663:87bb2918
2025-03-05 12:41:36After two years of using Standard Notes as my main note-taking app, I’m switching to Obsidian.
The $100 that Standard Notes charges for basic editing capabilities is difficult to justify, especially for someone paying in Brazilian Real and striving to make a living from writing. However, I will certainly miss its simplicity and cleaner interface.
It’s my impression that the developers are missing an opportunity to create a privacy-focused note-taking app tailored to the specific needs of writers, rather than general users.
Substack, for example, achieved such success because it targeted the distribution and monetization of writers’ work. But we need more tools focused not on distribution or monetization, but on the actual process—indeed, the various phases of the process—of creating texts. This is especially true for complex, long-form texts with different levels of argumentation, numerous written and multimedia sources, and cross-references to other works by the author.
It’s crucial that an app like this doesn’t feel overly complex, like Notion or Evernote, or so all-purpose, like Obsidian. And, of course, I’m not talking about a new full-fledged text editor like Scrivener.
Just a thought. Take note.
-
 @ 04c915da:3dfbecc9
2025-03-04 17:00:18
@ 04c915da:3dfbecc9
2025-03-04 17:00:18This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ d360efec:14907b5f
2025-03-03 05:40:07
@ d360efec:14907b5f
2025-03-03 05:40:07การวิเคราะห์แต่ละ Timeframe (TF):
-
TF 15m (Intraday):
- แนวโน้ม: Bearish (แต่เริ่มมีสัญญาณกลับตัวเล็กน้อย). ราคาเคยอยู่ใต้ EMA ทั้งสอง แต่เริ่มขยับขึ้นมาเหนือ EMA 50.
- SMC:
- มี Bearish OB ชัดเจนที่ ~93,000 (ทดสอบแล้วไม่ผ่านในวันที่ 1 มี.ค.).
- มี Bullish OB ที่ ~86,000-87,000 (ราคาลงไปทดสอบแล้วดีดกลับ).
- SSL: ~86,845, ~83,859 (ถูกกวาดไปแล้ว).
- BSL: ~92,669 (อาจเป็นเป้าหมายถัดไป).
- Trend Strength: เมฆยังเป็นสีแดง แต่เริ่มจางลง. มีลูกศร Buy เล็กๆ.
- กลยุทธ์ Day Trade (SMC):
- ระมัดระวัง: ตลาดมีความผันผวน. แนวโน้มหลักยังเป็นขาลง, แต่ระยะสั้นเริ่มมีแรงซื้อ.
- Option 1 (Aggressive): Buy เมื่อราคาย่อลงมาใกล้ Bullish OB (~87,000) หรือ EMA 50. ตั้ง Stop Loss ใต้ OB. เป้าหมายทำกำไรที่ BSL (~92,669) หรือ Bearish OB เดิม.
- Option 2 (Conservative): รอให้ราคา Breakout เหนือ Bearish OB (~93,000) อย่างชัดเจน แล้วค่อยพิจารณา Buy ตาม.
- Short: ถ้าจะ Short, รอให้ราคาขึ้นไปใกล้ Bearish OB อีกครั้ง แล้วเกิดสัญญาณ Bearish Reversal (เช่น Bearish Engulfing) ค่อย Short.
-
TF 4H (ระยะกลาง):
- แนวโน้ม: Bearish. ราคาอยู่ใต้ EMA ทั้งสอง, EMA 50 อยู่ใต้ EMA 200.
- SMC:
- Bearish OB ใหญ่: ~95,000-100,000.
- SSL: ~83,559.5, ~81,260.4, ~78,961.4 (เป้าหมายระยะกลาง-ยาว).
- BSL: 105,543.4
- Trend Strength: เมฆสีแดงเข้ม. สัญญาณ Sell.
- กลยุทธ์: เน้น Short. รอ Pullback ไปใกล้ EMA หรือ Bearish OB แล้วหาจังหวะ Short.
-
TF Day (ระยะยาว):
- แนวโน้ม: ยังคงเป็น Bearish, แต่เริ่มเห็นสัญญาณการชะลอตัว. ราคาหลุด EMA 200 ลงมา
- SMC: มี Order Block ใหญ่ที่ $90,000 - $100,000
- Trend Strength: เมฆเริ่มเปลี่ยนจากสีแดงเข้ม เป็นสีแดงจางลง. ยังไม่มีสัญญาณ Buy ที่ชัดเจน.
- กลยุทธ์: ยังไม่ควร Long. รอสัญญาณกลับตัวที่ชัดเจนกว่านี้ (เช่น Breakout เหนือ EMA 50, เกิด Bullish Divergence).
สรุปและข้อควรระวัง:
- แนวโน้มหลักของ BTC ยังคงเป็นขาลง (Bearish) ในทุก Timeframe.
- TF 15m เริ่มมีสัญญาณการกลับตัวระยะสั้น (Bullish Reversal) แต่ยังต้องระวัง เพราะยังอยู่ในแนวโน้มหลักขาลง.
- Smart Money อาจกำลังสะสม (Accumulation) ที่ระดับราคาปัจจุบัน.
- สิ่งที่ต้องระวัง: ข่าว, ความผันผวน, การ "กวาด" Stop Loss (Liquidity Sweep).
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-
-
 @ d360efec:14907b5f
2025-03-01 12:58:51
@ d360efec:14907b5f
2025-03-01 12:58:51ภาพรวม (Integrated Overview)
ถ้าพิจารณาทั้ง TF Daily, 4H, และ 15m (พร้อมข้อมูล Money Flow ที่เป็นลบในทุก TF) ราคาปัจจุบันประมาณ 84,579
การวิเคราะห์แบบรวม*
-
แนวโน้ม (Trend):
- Daily: ขาลง (Bearish) แม้ว่าราคาจะอยู่เหนือเส้นค่าเฉลี่ยเคลื่อนที่ (EMA) แต่ Money Flow ที่เป็นลบอย่างรุนแรง บ่งชี้ถึงแนวโน้มขาลง
- 4H: ขาลง (Bearish) Money Flow เป็นลบอย่างมาก และมี รูปแบบ Head and Shoulders ที่มีโอกาสเกิดขึ้น
- 15m: ขาลง (Bearish) Money Flow เป็นลบ
-
SMC & ICT (Smart Money Concepts & Inner Circle Trader):
- Buyside Liquidity: อยู่เหนือราคาสูงสุดปัจจุบัน ระดับราคาที่ อาจ เป็นแนวต้าน (จากกราฟ Daily): 90456.8, 92755.8, 95054.9, 97354.0, 99653.1, 101952.1, 104251.3, 106550.3, 109998.9, และ 117000.0 ใน TF 15m, Buyside Liquidity คือจุดสูงสุดของแท่งเทียนก่อนหน้า
- Sellside Liquidity: แนวรับสำคัญ: 80,000 (Neckline ของ Head and Shoulders ใน TF 4H, ตัวเลขกลม, แนวรับทางจิตวิทยา) แนวรับอื่นๆ: 83559.5, 81260.4, 78961.4, 76662.3, 74363.2, 72064.1, 69705.1, 67400.0, 66811.7, และ 65166.9 (จากกราฟ Daily) ใน TF 15m, Sellside Liquidity คือจุดต่ำสุดของแท่งเทียนก่อนหน้า
-
Money Flow:
- Daily: เป็นลบอย่างมาก (Strongly Negative)
- 4H: เป็นลบอย่างมาก (Strongly Negative)
- 15m: เป็นลบ (Negative)
- นี่คือตัวบ่งชี้ที่สำคัญที่สุดในขณะนี้ และเป็นขาลงในทุก Timeframe
-
EMA (Exponential Moving Averages):
- Daily: ราคาอยู่เหนือ EMA 50 และ 200 แต่ถูกหักล้างด้วย Money Flow ที่เป็นลบ
- 4H: ราคาอยู่เหนือ EMA 50 และ 200 แต่ถูกหักล้างด้วย Money Flow ที่เป็นลบ
- 15m: ราคาแกว่งตัวรอบ EMA 50, อยู่เหนือ EMA 200 แต่ถูกหักล้างด้วย Money Flow ที่เป็นลบ
-
Trend Strength (AlgoAlpha):
- Daily: เมฆ Ichimoku เป็นสีเทา (Neutral - เป็นกลาง)
- 4H: เมฆ Ichimoku เป็นสีเทา (Neutral - เป็นกลาง)
- 15m: เมฆ Ichimoku เป็นสีเทา (Neutral - เป็นกลาง)
-
Chart Patterns (รูปแบบกราฟ):
- Daily: ไม่มีรูปแบบที่ชัดเจน แต่มีการอ่อนตัวของราคา
- 4H: มีโอกาสเกิด รูปแบบ Head and Shoulders (กลับหัว) (Bearish - ขาลง)
- 15m: ไม่มีรูปแบบที่ชัดเจน แต่อาจเป็นส่วนหนึ่งของ Right Shoulder ใน TF 4H
กลยุทธ์ Day Trade (SMC-Based)
เนื่องจาก Money Flow ที่เป็นลบอย่างท่วมท้นในทุก Timeframes และรูปแบบ Head and Shoulders ที่มีโอกาสเกิดขึ้นใน TF 4H กลยุทธ์การซื้อขายที่สมเหตุสมผล เพียงอย่างเดียว คือ การป้องกันอย่างเข้มงวด โดยเน้นที่ การหลีกเลี่ยงสถานะ Long และพิจารณาสถานะ Short เฉพาะ เมื่อมีเงื่อนไขที่เข้มงวดมากเท่านั้น
-
Long (Buy): ไม่แนะนำโดยเด็ดขาด (Absolutely, unequivocally not recommended) การทำเช่นนี้จะเป็นการซื้อขายสวนทางกับแนวโน้มหลักและสัญญาณ Money Flow ที่ชัดเจน
-
Short (Sell):
- Entry (จุดเข้า): นี่คือการเทรด เดียว ที่ อาจ มีเหตุผลสนับสนุน, แต่ เฉพาะ เมื่อเงื่อนไข ทั้งหมด ต่อไปนี้เป็นจริง:
- รูปแบบ Head and Shoulders ใน TF 4H เสร็จสมบูรณ์ ด้วยการ Breakout ที่ชัดเจนใต้ Neckline (80,000-81,000)
- การ Breakout ใต้ Neckline เกิดขึ้นพร้อมกับ Volume ที่สูง
- Money Flow ใน ทั้งสาม Timeframes ยังคง เป็นลบอย่างมาก
- คุณมีสัญญาณ Bearish อื่นๆ ยืนยัน (เช่น รูปแบบแท่งเทียน Bearish, Bearish Divergence)
- Target (เป้าหมาย): ระดับ Sellside Liquidity (เช่น 78961.4, 76662.3)
- Stop Loss (จุดตัดขาดทุน): เหนือ Neckline หรือ Right Shoulder ทันที จำเป็นต้องมี Stop Loss ที่เข้มงวดอย่างยิ่ง
- Entry (จุดเข้า): นี่คือการเทรด เดียว ที่ อาจ มีเหตุผลสนับสนุน, แต่ เฉพาะ เมื่อเงื่อนไข ทั้งหมด ต่อไปนี้เป็นจริง:
-
No Trade (ไม่เทรด): เป็นตัวเลือกที่ ดีที่สุด สำหรับนักเทรด/นักลงทุนส่วนใหญ่ ความเสี่ยงที่จะเกิดการปรับฐานครั้งใหญ่มีสูงมาก
สรุป
สถานการณ์ของ BTC คือ Bearish อย่างมาก Money Flow ที่เป็นลบอย่างมากในทุก Timeframes เป็นปัจจัยสำคัญที่สุด ซึ่งมีน้ำหนักมากกว่าสัญญาณ Bullish ใดๆ ก่อนหน้านี้จาก EMA รูปแบบ Head and Shoulders ที่มีโอกาสเกิดขึ้นใน TF 4H ช่วยเพิ่มการยืนยันแนวโน้ม Bearish สถานะ Long ไม่สมเหตุสมผลอย่างยิ่ง สถานะ Short อาจ พิจารณาได้, แต่ ต้อง มีการยืนยันสัญญาณที่ชัดเจน ทั้งหมด และมีการบริหารความเสี่ยงที่เข้มงวดมาก "Wait and See" (รอดู) และการรักษาเงินทุนเป็นสิ่งสำคัญที่สุด
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-
-
 @ d360efec:14907b5f
2025-03-01 12:55:57
@ d360efec:14907b5f
2025-03-01 12:55:57$OKX:BTCUSDT.P
Overview (Integrated Overview)
All three provided timeframes (Daily, 4H, and 15m, all now confirmed to have negative Money Flow), The current price is approximately 84,579.
Integrated Analysis
-
Trend:
- Daily: Bearish. While the price is above the EMAs, the strongly negative Money Flow on the Daily chart overrides the EMA signal, indicating a bearish trend. The Ichimoku Cloud is neutral, further supporting the idea that the previous bullish trend is weakening.
- 4H: Bearish. Strongly negative Money Flow and a potential (but not yet confirmed) inverted Head and Shoulders pattern.
- 15m: Bearish. Negative Money Flow.
-
SMC & ICT (Smart Money Concepts & Inner Circle Trader):
- Buyside Liquidity: Above the current high. Potential resistance levels (derived from the Daily chart image, assuming it's from 2025): 90456.8, 92755.8, 95054.9, 97354.0, 99653.1, 101952.1, 104251.3, 106550.3, 109998.9, and 117000.0. On the 15m chart (though we are prioritizing the Daily and 4H now), Buyside Liquidity would be represented by recent swing highs.
- Sellside Liquidity: Key support: 80,000 (this is the approximate neckline of the potential Head and Shoulders pattern on the 4H chart, a round number, and a psychological support level). Other support levels (derived from the Daily chart image): 83559.5, 81260.4, 78961.4, 76662.3, 74363.2, 72064.1, 69705.1, 67400.0, 66811.7, and 65166.9. On the 15m chart, Sellside Liquidity would be represented by recent swing lows.
-
Money Flow:
- Daily: Strongly Negative. This is a major bearish signal.
- 4H: Strongly Negative. This reinforces the bearish signal and is consistent with the Daily chart.
- 15m: Negative. This confirms the short-term outflow of money.
- The consistently negative Money Flow across all timeframes is the most important and dominant indicator in this analysis.
-
EMA (Exponential Moving Averages):
- Daily: Price is above the EMA 50 (yellow) and EMA 200 (white). However, the strongly negative Money Flow overrides the bullish signal typically provided by the price being above the EMAs.
- 4H: Price is above the EMA 50 and EMA 200. Again, the strongly negative Money Flow overrides this.
- 15m: Price is oscillating around the EMA 50 and above the EMA 200. The negative Money Flow overrides this.
-
Trend Strength (AlgoAlpha Indicator):
- Daily: The Ichimoku Cloud is gray (Neutral). This is not a bullish signal and is consistent with the negative Money Flow.
- 4H: The Ichimoku Cloud is gray (Neutral).
- 15m: The Ichimoku Cloud is gray (Neutral).
-
Chart Patterns:
- Daily: No fully formed classic chart pattern. However, the recent price action shows a loss of upward momentum and the beginning of a potential downward move. This weakening price action, combined with the strongly negative Money Flow, is bearish.
- 4H: Potential inverted Head and Shoulders pattern. This is a bearish reversal pattern. It's crucial to understand that this pattern is not yet confirmed. Confirmation requires a decisive break below the neckline (approximately 80,000-81,000), with increased volume and continued negative Money Flow.
- 15m: No clearly defined classic chart pattern. The 15m price action is best understood as potentially forming the right shoulder of the 4H Head and Shoulders.
SMC-Based Day Trading Strategies
Given the overwhelmingly bearish evidence – primarily the strongly negative Money Flow across all timeframes, combined with the potential Head and Shoulders pattern on the 4H chart – the only justifiable trading strategy is extreme caution and a strong bias against long positions. Short positions have a slightly higher probability of success, but only under very specific conditions and with extremely tight risk management.
-
Long (Buy): Absolutely, unequivocally not recommended. There is no technical justification for entering a long position at this time. This would be trading directly against the dominant bearish signals.
-
Short (Sell):
- Entry: This is the only trade with any potential, and only if all of the following conditions are met:
- The Head and Shoulders pattern on the 4H chart fully completes with a decisive break below the neckline (80,000-81,000).
- The breakout below the neckline occurs on significantly increased volume.
- The Money Flow on all three timeframes (Daily, 4H, and 15m) remains strongly negative at the time of the breakout.
- Additional bearish confirmation is present (e.g., bearish candlestick patterns, bearish divergences on other oscillators like RSI or MACD – which we cannot see from the provided images).
- Target: Sellside Liquidity levels, derived from the Daily chart. Potential targets include, but are not limited to: 78961.4, 76662.3, 74363.2, and potentially lower.
- Stop Loss: Immediately above the neckline (after the breakout) or above the high of the right shoulder (if placing the trade before a confirmed neckline break – which is extremely risky). An extremely tight stop-loss is absolutely mandatory due to the inherent volatility of BTC and the potential for false breakouts.
- Entry: This is the only trade with any potential, and only if all of the following conditions are met:
-
No Trade (Cash): This is, by far, the best and most prudent option for the vast majority of traders and investors. The risk of a substantial price decline is extremely high, given the confluence of bearish signals. Preserving capital should be the primary objective.
Key Levels to Watch:
- 80,000 - 81,000 (4H Chart): This is the neckline of the potential Head and Shoulders pattern. A sustained break below this level, with the confirming factors listed above, would be a strong bearish signal.
- Money Flow on all chart:
Conclusion
The overall technical picture for BTC, strongly bearish. The dominant factor is the consistently and strongly negative Money Flow across all three timeframes. This overrides any seemingly bullish signals from the EMAs. The potential (but unconfirmed) Head and Shoulders pattern on the 4H chart adds further weight to the bearish case.
Long positions are completely unjustified and extremely risky. Short positions might be considered, but only with the strictest possible entry criteria, complete confirmation from multiple indicators, and extremely tight risk management. The "Wait and See" approach, prioritizing capital preservation, is the most prudent strategy for most market participants. This situation calls for extreme caution and a defensive posture.
Disclaimer: This analysis is a personal opinion. It is not financial advice. Trading and investing in cryptocurrencies involves significant risk. Always do your own research and consult with a qualified financial advisor before making any investment decisions.
-
-
 @ d360efec:14907b5f
2025-02-28 13:26:03
@ d360efec:14907b5f
2025-02-28 13:26:03ภาพรวมการวิเคราะห์ Bitcoin (BTC)
จากการตรวจสอบกราฟและอินดิเคเตอร์ใน Timeframe 15 นาที, 4 ชั่วโมง, และรายวัน (Day) พบว่า Bitcoin มีความผันผวนและมีแนวโน้มการเปลี่ยนแปลงที่น่าสนใจในแต่ละ Timeframe ดังรายละเอียดต่อไปนี้ค่ะ
อินดิเคเตอร์ที่ใช้ในการวิเคราะห์
- EMA (Exponential Moving Average):
- EMA 50 (สีเหลือง): แสดงแนวโน้มระยะสั้นของราคา
- EMA 200 (สีขาว): แสดงแนวโน้มระยะยาวของราคา
- SMC (Smart Money Concepts): แนวคิดการเทรดที่เน้นการวิเคราะห์พฤติกรรมของ "Smart Money" หรือผู้เล่นรายใหญ่ในตลาด
- ICT (Inner Circle Trader) Buyside & Sellside Liquidity: อินดิเคเตอร์ที่ระบุตำแหน่งสภาพคล่องฝั่งซื้อและฝั่งขาย ซึ่งเป็นเป้าหมายราคาที่น่าสนใจ
- Money Flow: อินดิเคเตอร์ที่แสดงทิศทางการไหลเข้าออกของเงินทุนในสินทรัพย์
- Trend Strength (🌟Introducing the Trend and Strength Signals indicator by AlgoAlpha!): อินดิเคเตอร์ที่ช่วยระบุแนวโน้มและความแข็งแกร่งของตลาด มีลักษณะเป็นเมฆและสัญญาณซื้อขาย
วิเคราะห์แนวโน้มและกลยุทธ์การเทรด
1. Timeframe 15 นาที (TF 15m)
- แนวโน้ม: ใน TF 15 นาที ราคา BTC มีความผันผวนในกรอบแคบ EMA 50 ตัดกับ EMA 200 บ่งบอกถึงความไม่แน่นอนของแนวโน้มในระยะสั้น
- สัญญาณอินดิเคเตอร์:
- Trend Strength: เกิดสัญญาณซื้อขาย (Buy/Sell Signal) แต่เมฆ (Cloud) ยังไม่ชัดเจน บ่งบอกถึงความแข็งแกร่งของแนวโน้มยังไม่เด่นชัด
- Money Flow: มีการสลับการไหลเข้าออกของเงินทุน สะท้อนถึงความไม่แน่นอนในระยะสั้น
- Buyside & Sellside Liquidity: อินดิเคเตอร์นี้จะช่วยระบุแนวรับแนวต้านใน TF สั้นๆ เพื่อใช้ในการพิจารณาจุดเข้าออก
- Chart Pattern: พิจารณารูปแบบ Chart Pattern ใน TF 15 นาที เช่น รูปแบบสามเหลี่ยม (Triangle) หรือรูปแบบธง (Flag) เพื่อหารูปแบบราคาที่อาจเกิดขึ้น
- กลยุทธ์ Day Trade (การเทรดรายวัน):
- กลยุทธ์: เน้นการเทรดในกรอบ Sideway โดยใช้แนวรับแนวต้านที่ระบุจาก Buyside & Sellside Liquidity และสัญญาณจาก Trend Strength ประกอบการตัดสินใจ
- SMC Setup: มองหา SMC Setup ใน TF 15 นาที เช่น Order Block หรือ Fair Value Gap บริเวณแนวรับแนวต้าน เพื่อหาจังหวะเข้าเทรดตามแนวโน้มระยะสั้น
- สิ่งที่ต้องระวัง: ความผันผวนสูงใน TF 15 นาที อาจทำให้เกิดสัญญาณหลอก ควรใช้ Stop Loss ที่เหมาะสม และบริหารความเสี่ยงอย่างเคร่งครัด
2. Timeframe 4 ชั่วโมง (TF 4H)
- แนวโน้ม: ใน TF 4 ชั่วโมง ราคา BTC มีแนวโน้มเป็นขาขึ้น EMA 50 อยู่เหนือ EMA 200 บ่งบอกถึงแนวโน้มขาขึ้นในระยะกลาง
- สัญญาณอินดิเคเตอร์:
- Trend Strength: เกิดเมฆสีเขียว (Green Cloud) และสัญญาณซื้อ (Buy Signal) บ่งบอกถึงแนวโน้มขาขึ้นที่แข็งแกร่ง
- Money Flow: เงินทุนไหลเข้าต่อเนื่อง สนับสนุนแนวโน้มขาขึ้น
- Buyside & Sellside Liquidity: อินดิเคเตอร์นี้จะช่วยระบุแนวรับแนวต้านที่สำคัญใน TF 4 ชั่วโมง เพื่อใช้ในการวางแผนการเทรดระยะกลาง
- Chart Pattern: พิจารณารูปแบบ Chart Pattern ใน TF 4 ชั่วโมง เช่น รูปแบบ Cup and Handle หรือรูปแบบ Ascending Triangle เพื่อยืนยันแนวโน้มขาขึ้น
- กลยุทธ์ Day Trade (การเทรดรายวัน) / Swing Trade (การเทรดระยะกลาง):
- กลยุทธ์: เน้นการเทรดตามแนวโน้มขาขึ้น โดยใช้ EMA 50 และแนวรับแนวต้านจาก Buyside & Sellside Liquidity เป็นจุดอ้างอิงในการเข้าเทรด
- SMC Setup: มองหา SMC Setup ใน TF 4 ชั่วโมง เช่น Break of Structure (BOS) หรือ Change of Character (CHOCH) เพื่อหาจังหวะเข้าเทรดตามแนวโน้มขาขึ้น
- สิ่งที่ต้องระวัง: การพักตัวของราคาในแนวโน้มขาขึ้น อาจทำให้เกิดการย่อตัวระยะสั้น ควรพิจารณาแนวรับที่แข็งแกร่ง และตั้ง Stop Loss เพื่อป้องกันความเสี่ยง
3. Timeframe รายวัน (TF Day)
- แนวโน้ม: ใน TF รายวัน ราคา BTC ยังคงอยู่ในแนวโน้มขาขึ้นระยะยาว EMA 50 อยู่เหนือ EMA 200 อย่างชัดเจน
- สัญญาณอินดิเคเตอร์:
- Trend Strength: เกิดเมฆสีเขียวขนาดใหญ่ (Large Green Cloud) และสัญญาณซื้อต่อเนื่อง (Continuous Buy Signal) บ่งบอกถึงแนวโน้มขาขึ้นระยะยาวที่แข็งแกร่งมาก
- Money Flow: เงินทุนไหลเข้าอย่างต่อเนื่องและแข็งแกร่ง สนับสนุนแนวโน้มขาขึ้นระยะยาว
- Buyside & Sellside Liquidity: อินดิเคเตอร์นี้จะช่วยระบุแนวรับแนวต้านที่สำคัญใน TF รายวัน เพื่อใช้ในการวางแผนการลงทุนระยะยาว
- Chart Pattern: พิจารณารูปแบบ Chart Pattern ใน TF รายวัน เช่น รูปแบบ Bullish Flag หรือรูปแบบ Wedge เพื่อยืนยันแนวโน้มขาขึ้นระยะยาว
- กลยุทธ์ Day Trade (การเทรดรายวัน) / Swing Trade (การเทรดระยะกลาง) / Long-Term Investment (การลงทุนระยะยาว):
- กลยุทธ์: เน้นการลงทุนระยะยาวตามแนวโน้มขาขึ้น โดยพิจารณาจังหวะเข้าซื้อเมื่อราคาย่อตัวลงมาบริเวณแนวรับสำคัญใน TF รายวัน
- SMC Setup: มองหา SMC Setup ใน TF รายวัน เช่น Institutional Order Flow เพื่อยืนยันแนวโน้มขาขึ้นระยะยาว
- สิ่งที่ต้องระวัง: ความเสี่ยงจากปัจจัยภายนอกที่อาจกระทบตลาด Cryptocurrency ในระยะยาว ควรติดตามข่าวสารและสถานการณ์ตลาดอย่างใกล้ชิด และกระจายความเสี่ยงในการลงทุน
สรุป
จากการวิเคราะห์ BTC ใน 3 Timeframe ด้วยอินดิเคเตอร์และ Chart Pattern พบว่า BTC ยังคงมีแนวโน้มขาขึ้นในระยะกลางและระยะยาว อย่างไรก็ตาม ในระยะสั้น TF 15 นาที ยังมีความผันผวนและไม่แน่นอน กลยุทธ์การเทรดที่เหมาะสมจะแตกต่างกันไปตาม Timeframe และเป้าหมายการเทรดของแต่ละบุคคล ควรพิจารณาความเสี่ยงและบริหารจัดการเงินทุนอย่างเหมาะสม
คำแนะนำเพิ่มเติม
- ศึกษาเพิ่มเติม: ควรศึกษาเพิ่มเติมเกี่ยวกับ SMC, ICT, และ Trend Strength Indicator เพื่อให้เข้าใจหลักการทำงานและนำไปประยุกต์ใช้ในการเทรดได้อย่างมีประสิทธิภาพ
- ทดลองบนบัญชี Demo: ทดลองกลยุทธ์ต่างๆ บนบัญชี Demo ก่อนนำไปใช้จริง เพื่อทดสอบความเข้าใจและปรับปรุงกลยุทธ์ให้เหมาะสมกับตนเอง
- ติดตามข่าวสาร: ติดตามข่าวสารและสถานการณ์ตลาด Cryptocurrency อย่างสม่ำเสมอ เพื่อประกอบการตัดสินใจในการเทรดและการลงทุน
Disclaimer (ข้อจำกัดความรับผิดชอบ):
การวิเคราะห์นี้มีวัตถุประสงค์เพื่อให้ข้อมูลเท่านั้น และเป็นความคิดเห็นส่วนบุคคล ไม่ใช่คำแนะนำทางการเงิน การลงทุนใน Cryptocurrency มีความเสี่ยงสูง นักลงทุนควรศึกษาข้อมูลด้วยตนเองและใช้ความระมัดระวังก่อนตัดสินใจลงทุน
- EMA (Exponential Moving Average):
-
 @ d360efec:14907b5f
2025-02-28 13:15:24
@ d360efec:14907b5f
2025-02-28 13:15:24$OKX:BTCUSDT.P
From checking the charts and indicators in 15-minute, 4-hour, and daily timeframes, it is found that Bitcoin is volatile and has interesting trend changes in each timeframe, as detailed below:
Trend Analysis and Trading Strategies
1. 15-Minute Timeframe (TF 15m)
- Trend: In the 15-minute TF, the BTC price is fluctuating in a narrow range. EMA 50 crossing with EMA 200 indicates short-term trend uncertainty.
- Indicator Signals:
- Trend Strength: Buy/Sell signals occur, but the cloud is not yet clear, indicating that the trend strength is not yet prominent.
- Money Flow: There is an alternating inflow and outflow of funds, reflecting short-term uncertainty.
- Buyside & Sellside Liquidity: This indicator helps identify support and resistance levels in short TFs to consider entry and exit points.
- Chart Pattern: Consider Chart Patterns in the 15-minute TF, such as Triangle or Flag patterns, to find possible price patterns.
- Day Trade Strategy:
- Strategy: Focus on trading in a Sideway range, using support and resistance levels identified by Buyside & Sellside Liquidity and signals from Trend Strength to make decisions.
- SMC Setup: Look for SMC Setups in the 15-minute TF, such as Order Blocks or Fair Value Gaps around support and resistance areas, to find short-term trend trading opportunities.
- Things to watch out for: High volatility in the 15-minute TF may cause false signals. Appropriate Stop Loss should be used and risk should be managed strictly.
2. 4-Hour Timeframe (TF 4H)
- Trend: In the 4-hour TF, the BTC price is trending upwards. EMA 50 is above EMA 200, indicating a medium-term uptrend.
- Indicator Signals:
- Trend Strength: A Green Cloud and Buy Signal occur, indicating a strong uptrend.
- Money Flow: Funds continue to flow in, supporting the uptrend.
- Buyside & Sellside Liquidity: This indicator helps identify important support and resistance levels in the 4-hour TF for medium-term trading planning.
- Chart Pattern: Consider Chart Patterns in the 4-hour TF, such as Cup and Handle or Ascending Triangle patterns, to confirm the uptrend.
- Day Trade / Swing Trade Strategy:
- Strategy: Focus on trading along the uptrend, using EMA 50 and support and resistance levels from Buyside & Sellside Liquidity as reference points for entering trades.
- SMC Setup: Look for SMC Setups in the 4-hour TF, such as Break of Structure (BOS) or Change of Character (CHOCH), to find trading opportunities along the uptrend.
- Things to watch out for: Price consolidation in an uptrend may cause short-term pullbacks. Strong support levels should be considered, and Stop Loss should be set to prevent risk.
3. Daily Timeframe (TF Day)
- Trend: In the Daily TF, the BTC price is still in a long-term uptrend. EMA 50 is clearly above EMA 200.
- Indicator Signals:
- Trend Strength: A Large Green Cloud and Continuous Buy Signal occur, indicating a very strong long-term uptrend.
- Money Flow: Funds are flowing in continuously and strongly, supporting the long-term uptrend.
- Buyside & Sellside Liquidity: This indicator helps identify important support and resistance levels in the Daily TF for long-term investment planning.
- Chart Pattern: Consider Chart Patterns in the Daily TF, such as Bullish Flag or Wedge patterns, to confirm the long-term uptrend.
- Day Trade / Swing Trade / Long-Term Investment Strategy:
- Strategy: Focus on long-term investment along the uptrend, considering buying opportunities when the price pulls back to important support levels in the Daily TF.
- SMC Setup: Look for SMC Setups in the Daily TF, such as Institutional Order Flow, to confirm the long-term uptrend.
- Things to watch out for: Risks from external factors that may affect the cryptocurrency market in the long term. Market news and situations should be closely monitored, and investment risk should be diversified.
Summary
From analyzing BTC in 3 Timeframes with indicators and Chart Patterns, it is found that BTC still has an uptrend in the medium and long term. However, in the short term, the 15-minute TF is still volatile and uncertain. Appropriate trading strategies will vary depending on the timeframe and individual trading goals. Risk should be considered and capital should be managed appropriately.
Additional Recommendations
- Further Study: Further study on SMC, ICT, and Trend Strength Indicator should be done to understand the working principles and apply them effectively in trading.
- Experiment on Demo Account: Experiment with various strategies on a Demo account before using them in real trading to test understanding and improve strategies to suit oneself.
- Follow News: Follow cryptocurrency market news and situations regularly to inform trading and investment decisions.
Disclaimer:
This analysis is for informational purposes only and represents a personal opinion. It is not financial advice. Investing in cryptocurrencies involves significant risk. Investors should conduct their own research and exercise due diligence before making any investment decisions.
-
 @ d360efec:14907b5f
2025-02-28 12:41:21
@ d360efec:14907b5f
2025-02-28 12:41:21$OKX:BTCUSDT.P Overview:
Based on the overall picture across the 3 timeframes (15m, 4H, Day), Bitcoin is in a bullish trend but is experiencing a short-term consolidation.
Analysis of each Timeframe:
-
TF 15m:
- SMC: The price is in a sideways consolidation phase after breaking out of a triangle pattern. There's potential to test the Buyside Liquidity around $64,000.
- ICT: The price is testing the EMA 50 (yellow) support. If it holds above this support, there's a chance for further upward movement.
- Buyside & Sellside Liquidity:
- Buyside Liquidity: $64,000
- Sellside Liquidity: $60,000 (around EMA 200 and the lower boundary of the sideways range)
- Money Flow: Positive, supporting the bullish trend.
- EMA: EMA 50 > EMA 200, a bullish signal.
- Trend Strength: Thick green cloud and buy signals indicate a strong uptrend.
- Chart Pattern: Triangle breakout.
-
TF 4H:
- SMC: The price is in a clear uptrend after breaking out of a significant resistance level.
- ICT: The price is holding strongly above both EMA 50 and EMA 200.
- Buyside & Sellside Liquidity:
- Buyside Liquidity: No significant resistance nearby.
- Sellside Liquidity: $58,000 (around EMA 50)
- Money Flow: Positive, supporting the bullish trend.
- EMA: EMA 50 > EMA 200, a bullish signal.
- Trend Strength: Green cloud and buy signals indicate an uptrend.
-
TF Day:
- SMC: The price is in a clear uptrend.
- ICT: The price is holding strongly above both EMA 50 and EMA 200.
- Buyside & Sellside Liquidity:
- Buyside Liquidity: No significant resistance nearby.
- Sellside Liquidity: $50,000 (around EMA 50)
- Money Flow: Positive, supporting the bullish trend.
- EMA: EMA 50 > EMA 200, a bullish signal.
- Trend Strength: Thick green cloud and buy signals indicate a strong uptrend.
Day Trade Strategy (SMC):
- Buy on Dip: Wait for the price to pull back towards the EMA 50 support on the 15m TF (around $61,500 - $62,000) or the lower boundary of the sideways range.
- Take Profit: Set a profit target at the Buyside Liquidity around $64,000.
- Stop Loss: Set a stop loss slightly below the Sellside Liquidity around $60,000.
Things to Watch Out For:
- Volatility: Bitcoin is highly volatile. Set your stop loss appropriately.
- False Breakout: Be cautious of false breakouts.
- News: Stay updated on news that may impact Bitcoin's price.
Summary:
Bitcoin is in a bullish trend across all timeframes but is experiencing a short-term consolidation. The recommended day trade strategy is "Buy on Dip," with a profit target of $64,000 and a stop loss slightly below $60,000.
Disclaimer: This analysis is for informational purposes only and represents a personal opinion. It is not financial advice. Investing in cryptocurrencies involves significant risk. Investors should conduct their own research and exercise due diligence before making any investment decisions.
-
-
 @ 6389be64:ef439d32
2025-02-27 21:32:12
@ 6389be64:ef439d32
2025-02-27 21:32:12GA, plebs. The latest episode of Bitcoin And is out, and, as always, the chicanery is running rampant. Let’s break down the biggest topics I covered, and if you want the full, unfiltered rant, make sure to listen to the episode linked below.
House Democrats’ MEME Act: A Bad Joke?
House Democrats are proposing a bill to ban presidential meme coins, clearly aimed at Trump’s and Melania’s ill-advised token launches. While grifters launching meme coins is bad, this bill is just as ridiculous. If this legislation moves forward, expect a retaliatory strike exposing how politicians like Pelosi and Warren mysteriously amassed their fortunes. Will it pass? Doubtful. But it’s another sign of the government’s obsession with regulating everything except itself.
Senate Banking’s First Digital Asset Hearing: The Real Target Is You
Cynthia Lummis chaired the first digital asset hearing, and—surprise!—it was all about control. The discussion centered on stablecoins, AML, and KYC regulations, with witnesses suggesting Orwellian measures like freezing stablecoin transactions unless pre-approved by authorities. What was barely mentioned? Bitcoin. They want full oversight of stablecoins, which is really about controlling financial freedom. Expect more nonsense targeting self-custody wallets under the guise of stopping “bad actors.”
Bank of America and PayPal Want In on Stablecoins
Bank of America’s CEO openly stated they’ll launch a stablecoin as soon as regulation allows. Meanwhile, PayPal’s CEO paid for a hat using Bitcoin—not their own stablecoin, Pi USD. Why wouldn’t he use his own product? Maybe he knows stablecoins aren’t what they’re hyped up to be. Either way, the legacy financial system is gearing up to flood the market with stablecoins, not because they love crypto, but because it’s a tool to extend U.S. dollar dominance.
MetaPlanet Buys the Dip
Japan’s MetaPlanet issued $13.4M in bonds to buy more Bitcoin, proving once again that institutions see the writing on the wall. Unlike U.S. regulators who obsess over stablecoins, some companies are actually stacking sats.
UK Expands Crypto Seizure Powers
Across the pond, the UK government is pushing legislation to make it easier to seize and destroy crypto linked to criminal activity. While they frame it as going after the bad guys, it’s another move toward centralized control and financial surveillance.
Bitcoin Tools & Tech: Arc, SatoChip, and Nunchuk
Some bullish Bitcoin developments: ARC v0.5 is making Bitcoin’s second layer more efficient, SatoChip now supports Taproot and Nostr, and Nunchuk launched a group wallet with chat, making multisig collaboration easier.
The Bottom Line
The state is coming for financial privacy and control, and stablecoins are their weapon of choice. Bitcoiners need to stay focused, keep their coins in self-custody, and build out parallel systems. Expect more regulatory attacks, but don’t let them distract you—just keep stacking and transacting in ways they can’t control.
🎧 Listen to the full episode here: https://fountain.fm/episode/PYITCo18AJnsEkKLz2Ks
💰 Support the show by boosting sats on Podcasting 2.0! and I will see you on the other side.
-
 @ d360efec:14907b5f
2025-02-25 10:16:18
@ d360efec:14907b5f
2025-02-25 10:16:18ภาพรวม BTCUSDT (OKX):
Bitcoin (BTCUSDT) แนวโน้มระยะยาว TF Day ยังคงเป็นขาลง แนวโน้มระยะกลาง TF 4H Sideway down และแนวโน้มระยะสั้น TF 15M Sideways Down
วิเคราะห์ทีละ Timeframe:
(1) TF Day (รายวัน):
- แนวโน้ม: ขาลง (Downtrend)
- SMC:
- Lower Highs (LH) และ Lower Lows (LL)
- Break of Structure (BOS) ด้านล่าง
- Liquidity:
- มี Sellside Liquidity (SSL) อยู่ใต้ Lows ก่อนหน้า
- มี Buyside Liquidity (BSL) อยู่เหนือ Highs ก่อนหน้า
- ICT:
- Order Block ราคาไม่สามารถผ่าน Order Block ได้
- EMA:
- ราคาอยู่ใต้ EMA 50 และ EMA 200
- Money Flow (LuxAlgo): * สีแดง
- Trend Strength (AlgoAlpha):
- สีแดง แสดงถึงแนวโน้มขาลง
- Chart Patterns: ไม่มีรูปแบบที่ชัดเจน
- Volume Profile: * Volume ค่อนข้างนิ่ง
- แท่งเทียน: แท่งเทียนล่าสุดเป็นสีแดง
- แนวรับ: บริเวณ Low ล่าสุด
- แนวต้าน: EMA 50, EMA 200 , Order Block
- สรุป: แนวโน้มขาลง
(2) TF4H (4 ชั่วโมง):
- แนวโน้ม: ขาลง (Downtrend)
- SMC:
- Lower Highs (LH) และ Lower Lows (LL)
- Break of Structure (BOS) ด้านล่าง
- Liquidity:
- มี SSL อยู่ใต้ Lows ก่อนหน้า
- มี BSL อยู่เหนือ Highs ก่อนหน้า
- ICT:
- Order Block ราคาไม่สามารถผ่าน Order Block ได้
- EMA:
- ราคาอยู่ใต้ EMA 50 และ EMA 200
- Money Flow (LuxAlgo):
- สีแดง แสดงถึงแรงขาย
- Trend Strength (AlgoAlpha): * สีแดง แสดงถึงแนวโน้มขาลง
- Chart Patterns: ไม่มีรูปแบบที่ชัดเจน
- Volume Profile: * Volume ค่อนข้างนิ่ง
- แนวรับ: บริเวณ Low ล่าสุด
- แนวต้าน: EMA 50, EMA 200, Order Block
- สรุป: แนวโน้มขาลง,
(3) TF15 (15 นาที):
- แนวโน้ม: Sideway Down
- SMC:
- Lower High (LH) และ Lower Lows (LL)
- Break of Structure (BOS) ด้านล่าง
- ICT:
- Order Block: ราคา Sideways ใกล้ Order Block
- EMA:
- EMA 50 และ EMA 200 เป็นแนวต้าน
- Money Flow (LuxAlgo):
- แดง
- Trend Strength (AlgoAlpha):
- แดง/ ไม่มีสัญญาณ
- Chart Patterns: ไม่มีรูปแบบที่ชัดเจน
- Volume Profile: Volume ค่อนข้างสูง
- แนวรับ: บริเวณ Low ล่าสุด
- แนวต้าน: EMA 50, EMA 200, Order Block
- สรุป: แนวโน้ม Sideways Down,
สรุปภาพรวมและกลยุทธ์ (BTCUSDT):
- แนวโน้มหลัก (Day): ขาลง
- แนวโน้มรอง (4H): ขาลง
- แนวโน้มระยะสั้น (15m): Sideways Down
- Liquidity: มี SSL ทั้งใน Day, 4H, และ 15m
- Money Flow: เป็นลบในทุก Timeframes
- Trend Strength: Day/4H/15m เป็นขาลง
- Chart Patterns: ไม่พบรูปแบบที่ชัดเจน
- กลยุทธ์:
- Wait & See (ดีที่สุด): รอความชัดเจน
- Short (เสี่ยง): ถ้าไม่สามารถ Breakout EMA/แนวต้านใน TF ใดๆ ได้ หรือเมื่อเกิดสัญญาณ Bearish Continuation
- ไม่แนะนำให้ Buy: จนกว่าจะมีสัญญาณกลับตัวที่ชัดเจนมากๆ
Day Trade & การเทรดรายวัน:
-
Day Trade (TF15):
- Short Bias: หาจังหวะ Short เมื่อราคาเด้งขึ้นไปทดสอบแนวต้าน (EMA, Order Block)
- Stop Loss: เหนือแนวต้านที่เข้า Short
- Take Profit: แนวรับถัดไป (Low ล่าสุด)
- ไม่แนะนำให้ Long
-
Swing Trade (TF4H):
- Short Bias: รอจังหวะ Short เมื่อราคาไม่สามารถผ่านแนวต้าน EMA หรือ Order Block ได้
- Stop Loss: เหนือแนวต้านที่เข้า Short
- Take Profit: แนวรับถัดไป
- ไม่แนะนำให้ Long
สิ่งที่ต้องระวัง:
- Sellside Liquidity (SSL): มีโอกาสสูงที่ราคาจะถูกลากลงไปแตะ SSL
- False Breakouts: ระวัง
- Volatility: สูง
Setup Day Trade แบบ SMC (ตัวอย่าง):
- ระบุ Order Block: หา Order Block ขาลง (Bearish Order Block) ใน TF15
- รอ Pullback: รอให้ราคา Pullback ขึ้นไปทดสอบ Order Block นั้น
- หา Bearish Entry:
- Rejection: รอ Price Action ปฏิเสธ Order Block
- Break of Structure: รอให้ราคา Break โครงสร้างย่อยๆ
- Money Flow: ดู Money Flow ให้เป็นสีแดง
- ตั้ง Stop Loss: เหนือ Order Block
- ตั้ง Take Profit: แนวรับถัดไป
คำแนะนำ:
- ความขัดแย้งของ Timeframes: ไม่มีแล้ว ทุก Timeframes สอดคล้องกัน
- Money Flow: เป็นลบในทุก Timeframes
- Trend Strength: เป็นลบ
- Order Block TF Day: หลุด Order Block ขาขึ้นแล้ว
- ถ้าไม่แน่ใจ อย่าเพิ่งเข้าเทรด
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-
 @ d360efec:14907b5f
2025-02-25 09:12:44
@ d360efec:14907b5f
2025-02-25 09:12:44$OKX:BTCUSDT.P
Overall Assessment:
Bitcoin (BTCUSDT) on OKX is currently showing a bearish trend across all analyzed timeframes (Daily, 4-Hour, and 15-Minute). While the long-term trend (Daily) was technically an uptrend, it has significantly weakened and broken key support levels, including a major bullish Order Block and the 50-period EMA. The 4-hour and 15-minute charts confirm the downtrend. This analysis focuses on identifying potential areas of Smart Money activity (liquidity pools and order blocks), assessing trend strength, and looking for any emerging chart patterns.
Detailed Analysis by Timeframe:
(1) TF Day (Daily):
- Trend: Downtrend
- SMC (Smart Money Concepts):
- The Higher Highs (HH) and Higher Lows (HL) structure is broken.
- Prior Breaks of Structure (BOS) to the upside, but now a significant and deep pullback/reversal is underway.
- Liquidity:
- Sellside Liquidity (SSL): Significant SSL rests below previous lows in the 85,000 - 90,000 range.
- Buyside Liquidity (BSL): BSL is present above the all-time high.
- ICT (Inner Circle Trader Concepts):
- Order Block: The price has broken below the prior bullish Order Block. This is a major bearish signal.
- FVG: No significant Fair Value Gap is apparent at the current price level.
- EMA (Exponential Moving Average):
- Price is below the 50-period EMA (yellow).
- The 200-period EMA (white) is the next major support level.
- Money Flow (LuxAlgo):
- A long red bar indicates strong and sustained selling pressure.
- Trend Strength (AlgoAlpha):
- Red cloud, indicating a downtrend. No buy/sell signals are present.
- Chart Patterns: No readily identifiable chart patterns are dominant.
- Volume Profile: Relatively low volume.
- Candlesticks: Recent candlesticks are red, confirming selling pressure.
- Support: EMA 200, 85,000-90,000 (SSL area).
- Resistance: EMA 50, Previous All-Time High.
- Summary: The Daily chart has shifted to a downtrend. The break below the Order Block and 50 EMA, combined with negative Money Flow and Trend Strength, are all strong bearish signals.
(2) TF4H (4-Hour):
- Trend: Downtrend.
- SMC:
- Lower Highs (LH) and Lower Lows (LL).
- BOS to the downside.
- Liquidity:
- SSL: Below previous lows.
- BSL: Above previous highs.
- ICT:
- Order Block: The price was rejected by a bearish Order Block.
- EMA:
- Price is below both the 50-period and 200-period EMAs (bearish).
- Money Flow (LuxAlgo):
- Predominantly red, confirming selling pressure.
- Trend Strength (AlgoAlpha):
- Red cloud, confirming downtrend.
- Chart Patterns: No readily identifiable chart patterns.
- Volume Profile: Relatively steady volume.
- Support: Recent lows.
- Resistance: EMA 50, EMA 200, Order Block.
- Summary: The 4-hour chart is in a confirmed downtrend. Money Flow and Trend Strength are bearish.
(3) TF15 (15-Minute):
* Trend: Downtrend / Sideways Down * SMC: * Lower Highs (LH) and Lower Lows (LL). * BOS to the downside. * ICT: * Order Block price is near to a bearish Order Block. * EMA: * The 50-period and 200-period EMAs are acting as resistance. * Money Flow (LuxAlgo): * Red * Trend Strength (AlgoAlpha): * Red/No signals * Chart Patterns: None * Volume Profile: * Relatively High Volume * Support: Recent lows. * Resistance: EMA 50, EMA 200, Order Block. * Summary: The 15-minute chart is clearly bearish, with price action, EMAs, and Money Flow all confirming the downtrend.
Overall Strategy and Recommendations (BTCUSDT):
- Primary Trend (Day): Downtrend
- Secondary Trend (4H): Downtrend.
- Short-Term Trend (15m): Downtrend/ Sideways Down.
- Liquidity: Significant SSL zones exist below the current price on all timeframes.
- Money Flow: Negative on all timeframes.
- Trend Strength: Bearish on Day,4H and 15m.
-
Chart Patterns: None identified.
-
Strategies:
- Wait & See (Best Option): The strong bearish momentum on all shorter timeframes.
-
Short (High Risk): This aligns with the 4H and 15m downtrends.
- Entry: On rallies towards resistance levels (EMAs on 15m/4H, previous support levels that have turned into resistance, Order Blocks).
- Stop Loss: Above recent highs on the chosen timeframe, or above a key resistance level.
- Target: The next support levels (recent lows on 15m, then potentially the SSL zones on the 4H and Daily charts).
-
Buy (Extremely High Risk - NOT Recommended): Do not attempt to buy until there are very strong and consistent bullish reversal signals across all timeframes.
Key Recommendations:
- Conflicting Timeframes: The conflict is resolved toward the downside. The Daily is weakening significantly.
- Money Flow: Consistently negative across all timeframes, a major bearish factor.
- Trend Strength: Bearish on Day,4h and 15m.
- Daily Order Block: The break of the bullish Order Block on the Daily chart is a significant bearish development.
- Sellside Liquidity (SSL): Be aware that Smart Money may target the SSL zones below. This increases the risk of stop-loss hunting.
- Risk Management: Due to the high uncertainty and volatility, strict risk management is absolutely critical. Use tight stop-losses, do not overtrade, and be prepared for rapid price swings.
- Volume: Confirm any breakout or breakdown with volume.
Day Trading and Intraday Trading Strategies:
-
Day Trade (TF15 focus):
- Short Bias: Given the current 15m downtrend and negative Money Flow, the higher probability is to look for shorting opportunities.
- Entry: Look for price to rally to resistance levels (EMAs, Order Blocks, previous support levels that have become resistance) and then show signs of rejection (bearish candlestick patterns, increasing volume on the downside).
- Stop Loss: Place a stop-loss order above the resistance level where you enter the short position.
- Take Profit: Target the next support level (recent lows).
- Avoid Long positions until there's a clear and confirmed bullish reversal on the 15m chart (break above EMAs, positive Money Flow, bullish market structure).
- Short Bias: Given the current 15m downtrend and negative Money Flow, the higher probability is to look for shorting opportunities.
-
Swing Trade (TF4H focus):
- Short Bias: The 4H chart is in a downtrend.
- Entry: Wait for price to rally to resistance levels (EMAs, Order Blocks) and show signs of rejection.
- Stop Loss: Above the resistance level where you enter the short position.
- Take Profit: Target the next support levels (e.g., the 200 EMA on the Daily chart, SSL zones).
- Avoid Long positions until there's a clear and confirmed bullish reversal on the 4H chart.
- Short Bias: The 4H chart is in a downtrend.
SMC Day Trade Setup Example (TF15 - Bearish):
- Identify Bearish Order Block: Locate a bearish Order Block on the TF15 chart (a bullish candle before a strong downward move).
- Wait for Pullback: Wait for the price to pull back up to test the Order Block (this may or may not happen).
- Bearish Entry:
- Rejection: Look for price action to reject the Order Block (e.g., a pin bar, engulfing pattern, or other bearish candlestick pattern).
- Break of Structure: Look for a break of a minor support level on a lower timeframe (e.g., 1-minute or 5-minute) after the price tests the Order Block. This confirms weakening bullish momentum.
- Money Flow: Confirm that Money Flow remains negative (red).
- Stop Loss: Place a stop-loss order above the Order Block.
- Take Profit: Target the next support level (e.g., recent lows) or a bullish Order Block on a higher timeframe.
In conclusion, BTCUSDT is currently in a high-risk, bearish environment. The "Wait & See" approach is strongly recommended for most traders. Shorting is the higher-probability trade at this moment, but only for experienced traders who can manage risk extremely effectively. Buying is not recommended at this time.
Disclaimer: This analysis is for informational purposes only and represents a personal opinion. It is not financial advice. Investing in cryptocurrencies involves significant risk. Investors should conduct their own research and exercise due diligence before making any investment decisions.
-
 @ 04c915da:3dfbecc9
2025-02-25 03:55:08
@ 04c915da:3dfbecc9
2025-02-25 03:55:08Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ d360efec:14907b5f
2025-02-24 11:33:16
@ d360efec:14907b5f
2025-02-24 11:33:16ภาพรวม BTCUSDT (OKX):
Bitcoin (BTCUSDT) ยังคงแสดงความผันผวนและแนวโน้มที่ไม่ชัดเจน แม้ว่าแนวโน้มระยะยาว (TF Day) จะยังคงมีลักษณะเป็นขาขึ้น (แต่อ่อนแรงลงอย่างมาก) แนวโน้มระยะกลาง (TF4H) และระยะสั้น (TF15) เป็นขาลง/Sideways Down การวิเคราะห์ครั้งนี้จะเน้นไปที่ SMC, ICT, และรูปแบบ Chart Patterns เพื่อเพิ่มความแม่นยำในการระบุแนวโน้มและจุดเข้า/ออก
วิเคราะห์ทีละ Timeframe:
(1) TF Day (รายวัน):
- แนวโน้ม: ขาขึ้น (Uptrend) อ่อนแรงลงอย่างมาก, มีความเสี่ยงที่จะเปลี่ยนแนวโน้ม
- SMC:
- Higher Highs (HH) และ Higher Lows (HL) เริ่มไม่ชัดเจน, ราคาหลุด Low ก่อนหน้า
- Break of Structure (BOS) ด้านบน แต่มีการปรับฐานที่รุนแรง
- Liquidity:
- มี Sellside Liquidity (SSL) อยู่ใต้ Lows ก่อนหน้า (บริเวณ 85,000 - 90,000)
- มี Buyside Liquidity (BSL) อยู่เหนือ High เดิม
- ICT:
- Order Block: ราคาหลุด Order Block ขาขึ้น
- FVG: ไม่มี FVG ชัดเจน
- EMA:
- ราคา หลุด EMA 50 (สีเหลือง) ลงมาแล้ว
- EMA 200 (สีขาว) เป็นแนวรับถัดไป
- Money Flow (LuxAlgo):
- สีแดงยาว แสดงถึงแรงขายที่แข็งแกร่ง
- Trend Strength (AlgoAlpha):
- สีแดง (เมฆแดง) แสดงถึงแนวโน้มขาลง และไม่มีสัญญาณซื้อ/ขายปรากฏ
- Chart Patterns: ไม่มีรูปแบบที่ชัดเจน
- Volume Profile: Volume ค่อนข้างเบาบาง
- แท่งเทียน: แท่งเทียนล่าสุดเป็นสีแดง แสดงถึงแรงขาย
- แนวรับ: EMA 200, บริเวณ 85,000 - 90,000 (SSL)
- แนวต้าน: EMA 50, High เดิม
- สรุป: แนวโน้มขาขึ้นอ่อนแรงลงอย่างมาก, สัญญาณอันตรายหลายอย่าง, Money Flow และ Trend Strength เป็นลบ, หลุด Order Block และ EMA 50
(2) TF4H (4 ชั่วโมง):
- แนวโน้ม: ขาลง (Downtrend)
- SMC:
- Lower Highs (LH) และ Lower Lows (LL)
- Break of Structure (BOS) ด้านล่าง
- Liquidity:
- มี SSL อยู่ใต้ Lows ก่อนหน้า
- มี BSL อยู่เหนือ Highs ก่อนหน้า
- ICT:
- Order Block: ราคาไม่สามารถผ่าน Order Block ขาลงได้
- EMA:
- ราคาอยู่ใต้ EMA 50 และ EMA 200
- Money Flow (LuxAlgo):
- สีแดง แสดงถึงแรงขาย
- Trend Strength (AlgoAlpha):
- แดง/ไม่มีสัญญาณ
- Chart Patterns: ไม่มีรูปแบบที่ชัดเจน
- Volume Profile: * Volume ค่อนข้างนิ่ง
- แนวรับ: บริเวณ Low ล่าสุด
- แนวต้าน: EMA 50, EMA 200, บริเวณ Order Block
- สรุป: แนวโน้มขาลงชัดเจน, แรงขายมีอิทธิพล
(3) TF15 (15 นาที):
- แนวโน้ม: Sideways Down (แกว่งตัวลง)
- SMC:
- Lower Highs (LH) และ Lower Lows (LL)
- Break of Structure (BOS) ด้านล่าง
- ICT:
- ราคา Sideway
- EMA:
- EMA 50 และ EMA 200 เป็นแนวต้าน
- Money Flow (LuxAlgo):
- แดง/เขียว สลับกัน
- Trend Strength (AlgoAlpha):
- สีแดง แสดงถึงแนวโน้มขาลง
- Chart Patterns: ไม่มีรูปแบบที่ชัดเจน
- Volume Profile: * Volume ค่อนข้างนิ่ง
- แนวรับ: บริเวณ Low ล่าสุด
- แนวต้าน: EMA 50, EMA 200
- สรุป: แนวโน้ม Sideways Down,
สรุปภาพรวมและกลยุทธ์ (BTCUSDT):
- แนวโน้มหลัก (Day): ขาขึ้น (อ่อนแรงลงอย่างมาก, เสี่ยงที่จะเปลี่ยนแนวโน้ม)
- แนวโน้มรอง (4H): ขาลง
- แนวโน้มระยะสั้น (15m): ขาลง/Sideways Down
- Liquidity: มี SSL ทั้งใน Day, 4H, และ 15m
- Money Flow: เป็นลบในทุก Timeframes
- Trend Strength: Day/15m เป็นขาลง, 4H Sideways
- Chart Patterns: ไม่พบรูปแบบที่ชัดเจน
- กลยุทธ์:
- Wait & See (ดีที่สุด): รอความชัดเจน
- Short (เสี่ยง): ถ้าไม่สามารถ Breakout EMA/แนวต้านใน TF ใดๆ ได้ หรือเมื่อเกิดสัญญาณ Bearish Continuation
- ไม่แนะนำให้ Buy: จนกว่าจะมีสัญญาณกลับตัวที่ชัดเจนมากๆ
Day Trade & การเทรดรายวัน:
-
Day Trade (TF15):
- Short Bias: หาจังหวะ Short เมื่อราคาเด้งขึ้นไปทดสอบแนวต้าน (EMA, Order Block)
- Stop Loss: เหนือแนวต้านที่เข้า Short
- Take Profit: แนวรับถัดไป (Low ล่าสุด)
- ไม่แนะนำให้ Long
-
Swing Trade (TF4H):
- Short Bias: รอจังหวะ Short เมื่อราคาไม่สามารถผ่านแนวต้าน EMA หรือ Order Block ได้
- Stop Loss: เหนือแนวต้านที่เข้า Short
- Take Profit: แนวรับถัดไป
- ไม่แนะนำให้ Long
สิ่งที่ต้องระวัง:
- Sellside Liquidity (SSL): มีโอกาสสูงที่ราคาจะถูกลากลงไปแตะ SSL
- False Breakouts: ระวัง
- Volatility: สูง
Setup Day Trade แบบ SMC (ตัวอย่าง):
- ระบุ Order Block: หา Order Block ขาลง (Bearish Order Block) ใน TF15
- รอ Pullback: รอให้ราคา Pullback ขึ้นไปทดสอบ Order Block นั้น
- หา Bearish Entry:
- Rejection: รอ Price Action ปฏิเสธ Order Block
- Break of Structure: รอให้ราคา Break โครงสร้างย่อยๆ
- Money Flow: ดู Money Flow ให้เป็นสีแดง
- ตั้ง Stop Loss: เหนือ Order Block
- ตั้ง Take Profit: แนวรับถัดไป
คำแนะนำ:
- ความขัดแย้งของ Timeframes: มีอยู่ แต่แนวโน้มระยะกลาง-สั้น เป็นลบ
- Money Flow: เป็นลบในทุก Timeframes
- Trend Strength: เป็นลบ
- Order Block TF Day: หลุด Order Block ขาขึ้นแล้ว
- ถ้าไม่แน่ใจ อย่าเพิ่งเข้าเทรด
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-
 @ d360efec:14907b5f
2025-02-24 10:49:26
@ d360efec:14907b5f
2025-02-24 10:49:26$OKX:BTCUSDT.P
Overall Assessment:
Bitcoin (BTCUSDT) on OKX continues to exhibit high volatility and an uncertain trend. While the long-term trend (Daily chart) is technically still an uptrend, it has weakened considerably. The 4-hour and 15-minute charts are in downtrends, creating conflicting signals. This analysis focuses on identifying potential areas of Smart Money activity (liquidity pools and order blocks), assessing trend strength, and identifying any relevant chart patterns.
Detailed Analysis by Timeframe:
(1) TF Day (Daily):
- Trend: Uptrend (Significantly Weakening, High Risk of Reversal).
- SMC (Smart Money Concepts):
- The Higher Highs (HH) and Higher Lows (HL) structure is becoming less defined. The recent price action has broken a previous low.
- Prior Breaks of Structure (BOS) to the upside, but the current pullback is very deep.
- Liquidity:
- Sellside Liquidity (SSL): Significant SSL rests below previous lows in the 85,000 - 90,000 range. This is a likely target for Smart Money.
- Buyside Liquidity (BSL): BSL is present above the all-time high.
- ICT (Inner Circle Trader Concepts):
- Order Block: The price has broken below the prior bullish Order Block (the large green candle before a significant up-move). This is a major bearish signal.
- FVG: No clear, significant Fair Value Gap is apparent at the current price level on the Daily chart.
- EMA (Exponential Moving Average):
- Price has broken below the 50-period EMA (yellow), a bearish signal.
- The 200-period EMA (white) is the next major support level.
- Money Flow (LuxAlgo):
- A long red bar indicates strong and sustained selling pressure.
- Trend Strength (AlgoAlpha):
- Red cloud indicates a downtrend. No buy/sell signals are present.
- Chart Patterns: No readily identifiable, classic chart patterns are apparent on the Daily chart.
- Volume Profile: Relatively low volume on the decline.
- Candlesticks: The most recent candlestick is red, confirming selling pressure.
- Support: EMA 200, 85,000-90,000 (SSL area).
- Resistance: EMA 50, Previous All-Time High.
- Summary: The Daily chart's uptrend is significantly weakening. The break below the 50 EMA and the bullish Order Block, combined with the negative Money Flow and bearish Trend Strength, are all major red flags. The SSL below is a key area to watch.
(2) TF4H (4-Hour):
- Trend: Downtrend.
- SMC:
- Lower Highs (LH) and Lower Lows (LL).
- BOS to the downside.
- Liquidity:
- SSL: Below previous lows.
- BSL: Above previous highs.
- ICT:
- Order Block: The price failed to break above a bearish Order Block.
- EMA:
- Price is below both the 50-period and 200-period EMAs (bearish).
- Money Flow (LuxAlgo):
- Predominantly red, confirming selling pressure.
- Trend Strength (AlgoAlpha):
- Red, indicating no particular trend or a sideways movement. No buy/sell signals.
- Chart Patterns: No readily identifiable, classic chart patterns are apparent.
- Volume Profile: Relatively consistent volume.
- Support: Recent lows.
- Resistance: EMA 50, EMA 200, Order Block.
- Summary: The 4-hour chart is in a confirmed downtrend. The Money Flow is bearish, price below both EMAs.
(3) TF15 (15-Minute):
- Trend: Downtrend / Sideways Down
- SMC:
- Lower Highs (LH) and Lower Lows (LL).
- BOS to the downside.
- ICT:
- Order Block Price could not break up the bearish Order Block.
- EMA:
- The 50-period and 200-period EMAs are acting as resistance.
- Money Flow (LuxAlgo):
- Red and Green
- Trend Strength (AlgoAlpha):
- Red cloud (Bearish)
- Chart Patterns: No readily identifiable, classic chart patterns are apparent.
- Volume Profile
- Relatively high volume.
- Support: Recent lows.
- Resistance: EMA 50, EMA 200, Order Block.
- Summary: The 15-minute chart is in a downtrend, with price action, EMAs, and Money Flow all confirming.
Overall Strategy and Recommendations (BTCUSDT):
- Primary Trend (Day): Uptrend (Significantly Weakening).
- Secondary Trend (4H): Downtrend.
- Short-Term Trend (15m): Downtrend/ Sideways Down.
- Liquidity: Significant SSL zones exist below the current price on all timeframes.
- Money Flow: Negative on all timeframes.
- Trend Strength: Bearish on 15m and Day, Sideway on 4H.
-
Chart Patterns: None identified.
-
Strategies:
-
Wait & See (Best Option): The conflicting signals and the strong bearish momentum on the shorter timeframes, combined with the weakening Daily chart, make waiting the most prudent approach. Look for:
- Bearish Confirmation: A decisive break below the recent lows on the 15m and 4H charts, with increasing volume and continued negative Money Flow. This would confirm the continuation of the downtrend.
- Bullish Confirmation: A strong, sustained break above the 15/4H EMAs and Order Block, a shift in the 15m/4H Money Flow to green.
-
Short (High Risk): This aligns with the 4H and 15m downtrends.
- Entry: On rallies towards resistance levels (EMAs on 15m/4H, previous support levels that have turned into resistance, Order Blocks).
- Stop Loss: Above recent highs on the chosen timeframe, or above a key resistance level.
- Target: The next support levels (recent lows on 15m, then potentially the SSL zones on the 4H and Daily charts).
-
Buy (Extremely High Risk - Not Recommended): Do not attempt to buy until there are very strong and consistent bullish reversal signals across all timeframes, including a definitive shift in market structure on the 4H and 15m charts, positive Money Flow, and a clear break above resistance levels.
-
Key Recommendations:
- Conflicting Timeframes: The primary conflict is now resolved toward the downside. The Daily is weakening significantly.
- Money Flow: Consistently negative across all timeframes, a major bearish factor.
- Trend Strength: Bearish on 15m and Day, Sideways on 4h.
- Daily Order Block: The break of the bullish Order Block on the Daily chart is a significant bearish development.
- Sellside Liquidity (SSL): Be aware that Smart Money may target the SSL zones below. This increases the risk of stop-loss hunting.
- Risk Management: Due to the high uncertainty and volatility, strict risk management is absolutely critical. Use tight stop-losses, do not overtrade, and be prepared for rapid price swings.
- Volume: Confirm any breakout or breakdown with volume.
Day Trading and Intraday Trading Strategies:
-
Day Trade (TF15 focus):
- Short Bias: Given the current 15m downtrend and negative Money Flow, the higher probability is to look for shorting opportunities.
- Entry: Look for price to rally to resistance levels (EMAs, Order Blocks, previous support levels that have become resistance) and then show signs of rejection (bearish candlestick patterns, increasing volume on the downside).
- Stop Loss: Place a stop-loss order above the resistance level where you enter the short position.
- Take Profit: Target the next support level (recent lows).
- Avoid Long positions until there's a clear and confirmed bullish reversal on the 15m chart (break above EMAs, positive Money Flow, bullish market structure).
- Short Bias: Given the current 15m downtrend and negative Money Flow, the higher probability is to look for shorting opportunities.
-
Swing Trade (TF4H focus):
- Short Bias: The 4H chart is in a downtrend.
- Entry: Wait for price to rally to resistance levels (EMAs, Order Blocks) and show signs of rejection.
- Stop Loss: Above the resistance level where you enter the short position.
- Take Profit: Target the next support levels (e.g., the 200 EMA on the Daily chart, SSL zones).
- Avoid Long positions until there's a clear and confirmed bullish reversal on the 4H chart.
- Short Bias: The 4H chart is in a downtrend.
SMC Day Trade Setup Example (TF15 - Bearish):
- Identify Bearish Order Block: Locate a bearish Order Block on the TF15 chart (a bullish candle before a strong downward move).
- Wait for Pullback: Wait for the price to pull back up to test the Order Block (this may or may not happen).
- Bearish Entry:
- Rejection: Look for price action to reject the Order Block (e.g., a pin bar, engulfing pattern, or other bearish candlestick pattern).
- Break of Structure: Look for a break of a minor support level on a lower timeframe (e.g., 1-minute or 5-minute) after the price tests the Order Block. This confirms weakening bullish momentum.
- Money Flow: Confirm that Money Flow remains negative (red).
- Stop Loss: Place a stop-loss order above the Order Block.
- Take Profit: Target the next support level (e.g., recent lows) or a bullish Order Block on a higher timeframe.
In conclusion, BTCUSDT is currently in a high-risk, bearish environment in the short-to-medium term. The "Wait & See" approach is strongly recommended for most traders. Shorting is the higher-probability trade at this moment, but only for experienced traders who can manage risk extremely effectively. Buying is not recommended at this time.
Disclaimer: This analysis is for informational purposes only and represents a personal opinion. It is not financial advice. Investing in cryptocurrencies involves significant risk. Investors should conduct their own research and exercise due diligence before making any investment decisions.
-
 @ e3ba5e1a:5e433365
2025-02-23 06:35:51
@ e3ba5e1a:5e433365
2025-02-23 06:35:51My wife and I have six children, making our house a household of eight people. Looking just at the eight of us, how many relationships exist? Well, as a first stab, we could look at how many connections exist between two unique individuals in this family. The mathematical term for this is “8 choose 2”, and the answer is 8*7/2, or 28.
Even that doesn’t really capture the answer though, because relationships aren’t just between two people. For example, when my wife and two oldest children are the only ones still awake after the younger kids go to bed, we’ll put on my mature TV shows that they’ll appreciate and watch together. It’s our own little subgroup within the group.
Based on that, we could have groups of 2, 3, 4, all the way up to 8, the group of all of us. If you do the math, this comes up to 247 different subgroups of 2 or more people. That’s a lot of groups for just 8 people.
As a father, this means I’ll never be able to fully understand every set of connections within my family. I may have a good understanding of my own relationship with each child. I also am closely aware of the relationship between our two youngest children, since they’re twins. And I could probably list 20 or so other noteworthy relationships. But I’ll never understand all of them.
For example, months ago I bought a game on Steam for my 3rd and 4th kids. I know they like to play games together, so it was a relationship that I thought I understood well. A few days ago I found out that my oldest had joined them in playing one of these games (Brotato). I’d made the purchase, given it to the kids, and it sparked new relationship and interaction structures without my involvement.
There’s no problem with the fact that I can’t track every interaction in my house. That’s healthy! The kids are able to discover ways of interacting beyond what I can teach them, learn everything from schoolwork to video games from each other, and overall become more healthy and well-adjusted adults (I hope).
And here’s the important part: the growth of the number of connections is massive as the number of participants increases. If we add in another participant, we have 502 groupings. At 10 total participants, it jumps to over 1,000. By the time we get to 100, we’re well into the trillions.
A mathematical and software term for this is combinatoric complexity, the massive increase in an output value based on a small increase in the input. The analysis I’m providing could be termed as part of graph theory (for connections of 2, looking at people as vertices and connections as edges) or set theory (unique subsets, allowing for larger group sizes). But regardless, the point is: the increase in complexity is huge as more people join.
Now consider the global economy. It’s over 8 billion people. There are so many people that the number of groupings is absurd to talk about. Nonetheless, massive numbers of these groupings naturally occur. There are family units, friend circles, individual connections, companies, project teams, sports teams, schools, classes, and millions more. These groups of people form new ways of interacting, express vastly different desires for goods and services, and are capable of producing wide varieties of goods and services themselves.
When you allow this system to run free, beauty emerges. Each node in the graph can manage its own connections. Each person is free to make his or her own decisions about association, what to spend time on, what to spend money on, and so on. Each person does so on their own judgement and world view.
Some of these people may make “dumb” decisions. They may “waste” their time and money on useless things. Except: who made that value judgement? Clearly not them, they decided it was worth it. No central planner has the right to override their will.
My point in all this is: as yet another of many reasons in the list of “why people should be free,” we have one more data point: pure math. Central planning will never scale. Central planning will never appreciate the individuality and desires of each person. Only by giving people the freedom to explore their connections to others, discover what they can produce and consume, explore their options, and ultimately make their own decisions, can we have any chance of creating a world where everyone can succeed.
-
 @ b8851a06:9b120ba1
2025-02-22 19:43:13
@ b8851a06:9b120ba1
2025-02-22 19:43:13The digital guillotine has fallen. The Bybit hack wasn’t just a theft—it was a surgical strike exposing the fatal flaw of “crypto” that isn’t Bitcoin. This wasn’t a bug. It was a feature of a system designed to fail.
Here’s how North Korea’s Lazarus Group stole $1.5B in ETH, why “decentralized finance” is a joke, and how Bitcoin remains the only exit from this circus.
I. The Heist: How Centralized “Crypto” Betrayed Its Users
A. The Multisig Mousetrap (Or: Why You’re Still Using a Bank)
Bybit’s Ethereum cold wallet used multisig, requiring multiple approvals for transactions. Sounds secure, right? Wrong. • The Con: Hackers didn’t pick the lock; they tricked the keyholders using a UI masking attack. The wallet interface showed “SEND TO BYBIT”, but the smart contract was whispering “SEND TO PYONGYANG.” • Bitcoin Parallel: Bitcoin’s multisig is enforced on hardware, not a website UI. No browser spoofing, no phishing emails—just raw cryptography.
Ethereum’s multisig is a vault with a touchscreen PIN pad. Bitcoin’s is a mechanical safe with a key only you hold. Guess which one got robbed?
B. Smart Contracts: Dumb as a Bag of Hammers
The thieves didn’t “hack” Ethereum—they exploited its smart contract complexity. • Bybit’s security depended on a Safe.global contract. Lazarus simply tricked Bybit into approving a malicious upgrade. • Imagine a vending machine that’s programmed to take your money but never give you a soda. That’s Ethereum’s “trustless” tech.
Why Bitcoin Wins: Bitcoin doesn’t do “smart contracts” in the Ethereum sense. Its scripting language is deliberately limited—less code, fewer attack vectors.
Ethereum is a Lego tower; Bitcoin is a granite slab. One topples, one doesn’t.
II. The Laundering: Crypto’s Dirty Little Secret
A. Mixers, Bridges, and the Art of Spycraft
Once the ETH was stolen, Lazarus laundered it at lightspeed: 1. Mixers (eXch) – Obfuscating transaction trails. 2. Bridges (Chainflip) – Swapping ETH for Bitcoin because that’s the only exit that matters.
Bitcoin Reality Check: Bitcoin’s privacy tools (like CoinJoin) are self-custodial—no third-party mixers. You keep control, not some “decentralized” website waiting to be hacked.
Ethereum’s “bridges” are burning rope ladders. Bitcoin’s privacy? An underground tunnel only you control.
B. The $1.5B Lie: “Decentralized” Exchanges Are a Myth
Bybit’s “cold wallet” was on Safe.global—a so-called “decentralized” custodian. Translation? A website with extra steps. • When Safe.global got breached, the private keys were stolen instantly. • “Decentralized” means nothing if your funds depend on one website, one server, one weak link.
Bitcoin’s Answer: Self-custody. Hardware wallets. Cold storage. No trusted third parties.
Using Safe.global is like hiding your life savings in a gym locker labeled “STEAL ME.”
III. The Culprits: State-Sponsored Hackers & Crypto’s Original Sin
A. Lazarus Group: Crypto’s Robin Hood (For Dictators)
North Korea’s hackers didn’t break cryptography—they broke people. • Phishing emails disguised as job offers. • Bribes & social engineering targeting insiders. • DeFi governance manipulation (because Proof-of-Stake is just shareholder voting in disguise).
Bitcoin’s Shield: No CEO to bribe. No “upgrade buttons” to exploit. No governance tokens to manipulate. Code is law—and Bitcoin’s law is written in stone.
Ethereum’s security model is “trust us.” Bitcoin’s is “verify.”
B. The $3B Elephant: Altcoins Fund Dictators
Since 2017, Lazarus has stolen $3B+ in crypto, funding North Korea’s missile program.
Why? Because Ethereum, Solana, and XRP are built on Proof-of-Stake (PoS)—which centralizes power in the hands of a few rich validators. • Bitcoin’s Proof-of-Work: Miners secure the network through energy-backed cryptography. • Altcoins’ Proof-of-Stake: Security is dictated by who owns the most tokens.
Proof-of-Stake secures oligarchs. Proof-of-Work secures money. That’s why Lazarus can drain altcoin treasuries but hasn’t touched Bitcoin’s network.
IV. Bybit’s Survival: A Centralized Circus
A. The Bailout: Banks 2.0
Bybit took bridge loans from “undisclosed partners” (read: Wall Street vultures). • Just like a traditional bank, Bybit printed liquidity out of thin air to stay solvent. • If that sounds familiar, it’s because crypto exchanges are just banks in hoodies.
Bitcoin Contrast: No loans. No bailouts. No “trust.” Just 21 million coins, mathematically secured.
Bybit’s solvency is a confidence trick. Bitcoin’s solvency is math.
B. The Great Withdrawal Panic
Within hours, 350,000+ users scrambled to withdraw funds.
A digital bank run—except this isn’t a bank. It’s an exchange that pretended to be decentralized.
Bitcoin fixes this: your wallet isn’t an IOU. It’s actual money.
Bybit = a TikTok influencer promising riches. Bitcoin = the gold in your basement.
V. The Fallout: Regulators vs Reality
A. ETH’s 8% Crash vs Bitcoin’s Unshakable Base
Ethereum tanked because it’s a tech stock, not money. Bitcoin? Dropped 2% and stabilized.
No CEO, no headquarters, no attack surface.
B. The Regulatory Trap
Now the bureaucrats come in demanding: 1. Wallet audits (they don’t understand public ledgers). 2. Mixer bans (criminalizing privacy). 3. KYC everything (turning crypto into a surveillance state).
Bitcoin’s Rebellion: You can’t audit what’s already transparent. You can’t ban what’s unstoppable.
VI. Conclusion: Burn the Altcoins, Stack the Sats
The Bybit hack isn’t a crypto problem. It’s an altcoin problem.
Ethereum’s smart contracts, DeFi bridges, and “decentralized” wallets are Swiss cheese for hackers. Bitcoin? A titanium vault.
The Only Lessons That Matter:
✅ Multisig isn’t enough unless it’s Bitcoin’s hardware-enforced version. ✅ Complexity kills—every altcoin “innovation” is a security risk waiting to happen.
Lazarus Group won this round because “crypto” ignored Bitcoin’s design. The solution isn’t better regulations—it’s better money.
Burn the tokens. Unplug the servers. Bitcoin is the exit.
Take your money off exchanges. Be sovereign.
-
 @ 6e0ea5d6:0327f353
2025-02-21 18:15:52
@ 6e0ea5d6:0327f353
2025-02-21 18:15:52"Malcolm Forbes recounts that a lady, wearing a faded cotton dress, and her husband, dressed in an old handmade suit, stepped off a train in Boston, USA, and timidly made their way to the office of the president of Harvard University. They had come from Palo Alto, California, and had not scheduled an appointment. The secretary, at a glance, thought that those two, looking like country bumpkins, had no business at Harvard.
— We want to speak with the president — the man said in a low voice.
— He will be busy all day — the secretary replied curtly.
— We will wait.
The secretary ignored them for hours, hoping the couple would finally give up and leave. But they stayed there, and the secretary, somewhat frustrated, decided to bother the president, although she hated doing that.
— If you speak with them for just a few minutes, maybe they will decide to go away — she said.
The president sighed in irritation but agreed. Someone of his importance did not have time to meet people like that, but he hated faded dresses and tattered suits in his office. With a stern face, he went to the couple.
— We had a son who studied at Harvard for a year — the woman said. — He loved Harvard and was very happy here, but a year ago he died in an accident, and we would like to erect a monument in his honor somewhere on campus.— My lady — said the president rudely —, we cannot erect a statue for every person who studied at Harvard and died; if we did, this place would look like a cemetery.
— Oh, no — the lady quickly replied. — We do not want to erect a statue. We would like to donate a building to Harvard.
The president looked at the woman's faded dress and her husband's old suit and exclaimed:
— A building! Do you have even the faintest idea of how much a building costs? We have more than seven and a half million dollars' worth of buildings here at Harvard.
The lady was silent for a moment, then said to her husband:
— If that’s all it costs to found a university, why don’t we have our own?
The husband agreed.
The couple, Leland Stanford, stood up and left, leaving the president confused. Traveling back to Palo Alto, California, they established there Stanford University, the second-largest in the world, in honor of their son, a former Harvard student."
Text extracted from: "Mileumlivros - Stories that Teach Values."
Thank you for reading, my friend! If this message helped you in any way, consider leaving your glass “🥃” as a token of appreciation.
A toast to our family!
-
 @ d360efec:14907b5f
2025-02-21 10:48:17
@ d360efec:14907b5f
2025-02-21 10:48:17Overall Assessment:
Bitcoin (BTCUSDT) on OKX remains highly volatile and the overall trend is uncertain. While the long-term trend (Daily chart) is technically still an uptrend, it has weakened significantly. The 4-hour and 15-minute charts are in confirmed downtrends. This analysis focuses on identifying key levels where Smart Money might be active and assessing trend strength.
Detailed Analysis by Timeframe:
(1) TF Day (Daily): https://www.tradingview.com/x/o9YgoBlr/
- Trend: Uptrend (Significantly Weakening, at high risk of reversing).
- SMC (Smart Money Concepts):
- Higher Highs (HH) and Higher Lows (HL) structure is becoming less defined and broken. The recent price action has broken previous lows.
- Prior Breaks of Structure (BOS) to the upside, but now a significant and deep pullback is underway.
- Liquidity:
- Sellside Liquidity (SSL): Significant SSL rests below previous lows in the 85,000 - 90,000 range. This is a likely target for Smart Money.
- Buyside Liquidity (BSL): BSL is present above the all-time high.
- ICT (Inner Circle Trader Concepts):
- Order Block: The price has broken below the prior bullish Order Block (the large green candle before a significant up-move). This is a major bearish signal.
- EMA (Exponential Moving Average):
- Price has broken below the 50-period EMA (yellow), a bearish signal.
- The 200-period EMA (white) is the next major support level.
- Money Flow (LuxAlgo):
- A long red bar indicates strong selling pressure.
- Trend Strength (AlgoAlpha):
- Red Cloud indicating Downtrend, No Buy/Sell Signal.
- Volume Profile: Relatively low volume on the recent decline.
- Candlesticks: The most recent candlestick is red, confirming selling pressure.
- Support: EMA 200, 85,000-90,000 (SSL area).
- Resistance: EMA 50, Previous All-Time High.
- Summary: The Daily chart's uptrend is significantly weakening. The break below the 50 EMA and the bullish Order Block, combined with the negative Money Flow and bearish Trend Strength, are all major warning signs. The SSL below is a key area to watch.
(2) TF4H (4-Hour): https://www.tradingview.com/x/0sGC0Gny/
- Trend: Downtrend.
- SMC:
- Lower Highs (LH) and Lower Lows (LL).
- BOS to the downside.
- Liquidity:
- SSL: Below previous lows.
- BSL: Above previous highs.
- ICT:
- Order Block: The price was rejected by a bearish order Block
- EMA:
- Price is below both the 50-period and 200-period EMAs (bearish).
- Money Flow (LuxAlgo):
- Predominantly red, confirming selling pressure.
- Trend Strength (AlgoAlpha):
- Green Cloud But No Buy/Sell Signal. Indicates Sideway
- Volume Profile: * Relatively high volume.
- Support: Recent lows.
- Resistance: EMA 50, EMA 200, Order Block.
- Summary: The 4-hour chart is in a confirmed downtrend. The Money Flow is bearish, price below both EMAs.
(3) TF15 (15-Minute): https://www.tradingview.com/x/c7kIbqU0/
- Trend: Downtrend (but showing some signs of consolidation/sideways movement).
- SMC:
- Lower Highs (LH) and Lower Lows (LL) - but with slightly higher lows recently.
- BOS to the downside.
- ICT:
- Order Block Price could not break up the bearish Order Block.
- EMA:
- The 50-period and 200-period EMAs are acting as resistance.
- Money Flow (LuxAlgo):
- Alternating red and green, predominantly red.
- Trend Strength (AlgoAlpha):
- Red Cloud (Bearish), BUT there's a bullish divergence (price made a lower low, but the Trend Strength indicator made a higher low). This is a potential early warning sign, but needs strong confirmation.
- Volume Profile:
- Relatively high Volume
- Support: Recent lows.
- Resistance: EMA 50, EMA 200, Order Block.
- Summary: The 15-minute chart is in a downtrend, although with very tentative signs of stabilization. The bullish divergence on the Trend Strength is noteworthy, but not a buy signal on its own.
Overall Strategy and Recommendations (BTCUSDT):
- Primary Trend (Day): Uptrend (Significantly Weakening).
- Secondary Trend (4H): Downtrend.
- Short-Term Trend (15m): Downtrend (Potential Early Reversal Signals).
- Liquidity: Significant SSL zones exist below the current price on all timeframes.
- Money Flow: Negative on all timeframes.
-
Trend Strength: Bearish on Day and 15m. Sideway on 4H.
-
Strategies:
-
Wait & See (Best Option): The conflicting signals and the strong bearish momentum on the shorter timeframes, combined with the weakening Daily chart, make waiting the most prudent approach. Look for:
- Bearish Confirmation: A decisive break below the recent lows on the 15m and 4H charts, with increasing volume and continued negative Money Flow. This would confirm the continuation of the downtrend.
- Bullish Confirmation: A strong, sustained break above the 15m EMAs, a shift in the 15m Money Flow to green, and a bullish signal on the 4H Trend Strength, and price holding above EMAs and ideally reclaiming the Daily Order Block.
-
Short (High Risk): This aligns with the 4H and 15m downtrends.
- Entry: On rallies towards resistance levels (EMAs on 15m/4H, previous support levels that have turned into resistance).
- Stop Loss: Above recent highs on the chosen timeframe.
- Target: The next support levels (recent lows on 15m, then potentially the SSL zones on the 4H and Daily charts).
-
Buy (Extremely High Risk - Not Recommended): Do not attempt to buy until there are very strong and consistent bullish reversal signals across all timeframes, including a definitive shift in market structure on the 4H and 15m charts, positive Money Flow, and a clear break above resistance levels. The bullish divergence on the 15m Trend Strength is not sufficient on its own.
-
Key Recommendations:
- Conflicting Timeframes: The primary conflict is now resolved toward the downside. The Daily is weakening significantly.
- Money Flow: Consistently negative, a major bearish factor.
- Trend Strength: Bearish on Day and 15, Sideways on 4H, but the divergence on the 15m is a potential early warning.
- Daily Order Block: The break of the bullish Order Block is a significant bearish development.
- Sellside Liquidity (SSL): Be aware that Smart Money may target the SSL zones below. This increases the risk of stop-loss hunting.
- Risk Management: Due to the high uncertainty and volatility, strict risk management is absolutely critical. Use tight stop-losses, do not overtrade, and be prepared for rapid price swings.
- Volume: Confirm any breakout or breakdown with volume.
Day Trading and Intraday Trading Strategies:
-
Day Trade (TF15 focus):
- Short Bias: Given the current 15m downtrend and negative Money Flow, the higher probability is to look for shorting opportunities.
- Entry: Look for price to rally to resistance levels (EMAs, Order Blocks, previous support levels that have become resistance) and then show signs of rejection (bearish candlestick patterns, increasing volume on the downside).
- Stop Loss: Place a stop-loss order above the resistance level where you enter the short position.
- Take Profit: Target the next support level (recent lows).
- Be very cautious: The bullish divergence on the Trend Strength indicator suggests a potential bounce could occur. Don't be aggressive with shorts until this divergence is invalidated.
- Avoid Long positions: Until there's a clear and confirmed bullish reversal on the 15m chart (break above EMAs, positive Money Flow, bullish market structure).
- Short Bias: Given the current 15m downtrend and negative Money Flow, the higher probability is to look for shorting opportunities.
-
Swing Trade (TF4H focus):
- Short Bias: The 4H chart is in a downtrend.
- Entry: Wait for price to rally to resistance levels (EMAs, Order Blocks) and show signs of rejection.
- Stop Loss: Above the resistance level where you enter the short position.
- Take Profit: Target the next support levels (e.g., the 200 EMA on the Daily chart, SSL zones).
- Avoid Long positions: Until there's a clear and confirmed bullish reversal on the 4H chart.
- Short Bias: The 4H chart is in a downtrend.
SMC Day Trade Setup Example (TF15 - Bearish):
- Identify Bearish Order Block: Locate a bearish Order Block on the TF15 chart (a bullish candle before a strong downward move). We have identified this in previous analyses.
- Wait for Pullback: Wait for the price to pull back up to test the Order Block (this may or may not happen).
- Bearish Entry:
- Rejection: Look for price action to reject the Order Block (e.g., a pin bar, engulfing pattern, or other bearish candlestick pattern).
- Break of Structure: Look for a break of a minor support level on a lower timeframe (e.g., 1-minute or 5-minute) after the price tests the Order Block.
- Money Flow: Confirm that Money Flow remains negative (red).
- Stop Loss: Place a stop-loss order above the Order Block.
- Take Profit: Target the next support level (e.g., recent lows) or a bullish Order Block on a higher timeframe.
In conclusion, BTCUSDT is currently in a high-risk, bearish environment in the short-to-medium term. The "Wait & See" approach is strongly recommended for most traders. Shorting is the higher-probability trade at this moment, but only for experienced traders who can manage risk extremely effectively. Buying is not recommended at this time.
Disclaimer: This analysis is for informational purposes only and represents a personal opinion. It is not financial advice. Investing in cryptocurrencies involves significant risk. Investors should conduct their own research and exercise due diligence before making any investment decisions.
-
 @ d360efec:14907b5f
2025-02-21 10:39:03
@ d360efec:14907b5f
2025-02-21 10:39:03ภาพรวม BTCUSDT (OKX):
Bitcoin (BTCUSDT) ยังคงมีความผันผวนและแนวโน้มที่ไม่ชัดเจน แม้ว่า TF Day จะยังคงแสดงโครงสร้างตลาดที่เป็นขาขึ้น แต่ ก็เริ่มอ่อนแรงลงอย่างเห็นได้ชัด แนวโน้ม TF4H และ TF15 เป็น Sideway Down
วิเคราะห์ทีละ Timeframe:
(1) TF Day (รายวัน): https://www.tradingview.com/x/IVA4uegL/
- แนวโน้ม: ขาขึ้น (Uptrend) อ่อนแรงลงอย่างมาก, มีความเสี่ยงที่จะเปลี่ยนแนวโน้ม
- SMC:
- Higher Highs (HH) และ Higher Lows (HL) เริ่มไม่ชัดเจน, ราคาหลุด Low ก่อนหน้า
- Break of Structure (BOS) ด้านบน แต่มีการปรับฐานที่รุนแรง
- Liquidity:
- มี Sellside Liquidity (SSL) อยู่ใต้ Lows ก่อนหน้า (บริเวณ 85,000 - 90,000)
- มี Buyside Liquidity (BSL) อยู่เหนือ High เดิม
- ICT:
- Order Block: ราคาหลุด Order Block ขาขึ้น
- EMA:
- ราคา หลุด EMA 50 (สีเหลือง) ลงมาแล้ว
- EMA 200 (สีขาว) เป็นแนวรับถัดไป
- Money Flow (LuxAlgo):
- สีแดงยาว แสดงถึงแรงขายที่แข็งแกร่ง
- Trend Strength (AlgoAlpha):
- สีแดง (เมฆแดง) แสดงถึงแนวโน้มขาลง และไม่มีสัญญาณซื้อ/ขายปรากฏ
- Volume Profile: Volume ค่อนข้างเบาบาง
- แท่งเทียน: แท่งเทียนล่าสุดเป็นสีแดง แสดงถึงแรงขาย
- แนวรับ: EMA 200, บริเวณ 85,000 - 90,000 (SSL)
- แนวต้าน: EMA 50, High เดิม
- สรุป: แนวโน้มขาขึ้นอ่อนแรงลงอย่างมาก, สัญญาณอันตรายหลายอย่าง, Money Flow และ Trend Strength เป็นลบ, หลุด Order Block และ EMA 50
(2) TF4H (4 ชั่วโมง): https://www.tradingview.com/x/BP0BDAts/
- แนวโน้ม: Sideway Down
- SMC:
- Lower Highs (LH) และ Lower Lows (LL)
- Break of Structure (BOS) ด้านล่าง
- Liquidity:
- มี SSL อยู่ใต้ Lows ก่อนหน้า
- มี BSL อยู่เหนือ Highs ก่อนหน้า
- ICT:
- Order Block: ราคาไม่สามารถผ่าน Order Block ขาลงได้ และราคากำลังทดสอบ Order Block ขาขึ้น
- EMA:
- ราคาอยู่ใต้ EMA 50 และ EMA 200
- Money Flow (LuxAlgo):
- สีแดง แสดงถึงแรงขาย
- Trend Strength (AlgoAlpha):
- เขียว/ไม่มีสัญญาณ แสดงถึงแนวโน้ม Sideway
- Volume Profile: * Volume ค่อนข้างสูง
- แนวรับ: บริเวณ Low ล่าสุด, Order Block
- แนวต้าน: EMA 50, EMA 200, บริเวณ Order Block
- สรุป: แนวโน้ม Sideway Down, แรงขายมีอิทธิพล
(3) TF15 (15 นาที): (https://www.tradingview.com/x/c7kIbqU0/)
- แนวโน้ม: ขาลง (Downtrend) แต่เริ่มเห็นสัญญาณ Sideways
- SMC:
- Lower Highs (LH) และ Lower Lows (LL) เริ่มเห็นการยก Low เล็กน้อย
- Break of Structure (BOS) ด้านล่าง
- ICT:
- Order Block: ราคา Sideways ใกล้ Order Block
- EMA:
- EMA 50 และ EMA 200 เป็นแนวต้าน
- Money Flow (LuxAlgo):
- แดงสลับเขียว
- Trend Strength (AlgoAlpha):
- สีแดง (เมฆแดง) แสดงถึงแนวโน้มขาลง แต่มีสัญญาณ Bullish Divergence (ราคาทำ Lower Low แต่ Trend Strength ยก Low)
- Volume Profile: * Volume ค่อนข้างสูง
- แนวรับ: บริเวณ Low ล่าสุด
- แนวต้าน: EMA 50, EMA 200, Order Block
- สรุป: แนวโน้มขาลง, เริ่มพักตัว, Money Flow เริ่มมีความไม่แน่นอน
สรุปภาพรวมและกลยุทธ์ (BTCUSDT):
- แนวโน้มหลัก (Day): ขาขึ้น (อ่อนแรงลงอย่างมาก, เสี่ยงที่จะเปลี่ยนแนวโน้ม)
- แนวโน้มรอง (4H): Sideway Down
- แนวโน้มระยะสั้น (15m): ขาลง (เริ่มพักตัว, มี Divergence)
- Liquidity: มี SSL ทั้งใน Day, 4H, และ 15m
- Money Flow: เป็นลบในทุก Timeframes
- Trend Strength: Day/15m เป็นขาลง, 4H Sideway
- กลยุทธ์:
- Wait & See (ดีที่สุด): รอความชัดเจน
- Short (เสี่ยง): ถ้าไม่สามารถ Breakout EMA/แนวต้านใน TF ใดๆ ได้ หรือเมื่อเกิดสัญญาณ Bearish Continuation
- ไม่แนะนำให้ Buy: จนกว่าจะมีสัญญาณกลับตัวที่ชัดเจนมากๆ
Day Trade & การเทรดรายวัน:
-
Day Trade (TF15):
- Short Bias: หาจังหวะ Short เมื่อราคาเด้งขึ้นไปทดสอบแนวต้าน (EMA, Order Block)
- Stop Loss: เหนือแนวต้านที่เข้า Short
- Take Profit: แนวรับถัดไป (Low ล่าสุด)
- ระวัง: Bullish Divergence ใน Trend Strength
- ไม่แนะนำให้ Long
-
Swing Trade (TF4H):
- Short Bias: รอจังหวะ Short เมื่อราคาไม่สามารถผ่านแนวต้าน EMA หรือ Order Block ได้
- Stop Loss: เหนือแนวต้านที่เข้า Short
- Take Profit: แนวรับถัดไป
- ไม่แนะนำให้ Long
สิ่งที่ต้องระวัง:
- Sellside Liquidity (SSL): มีโอกาสสูงที่ราคาจะถูกลากลงไปแตะ SSL
- False Breakouts: ระวัง
- Volatility: สูง
- Divergence (TF15): อาจเป็นสัญญาณเริ่มต้นของการกลับตัว แต่ต้องรอการยืนยัน
- Trend Strength (TF4H): ไม่มีสัญญาณซื้อ/ขาย ต้องระวัง
Setup Day Trade แบบ SMC (ตัวอย่าง):
- ระบุ Order Block: หา Order Block ขาลง (Bearish Order Block) ใน TF15 (แท่งเทียนสีเขียวก่อนที่ราคาจะลงแรง)
- รอ Pullback: รอให้ราคา Pullback ขึ้นไปทดสอบ Order Block นั้น
- หา Bearish Entry:
- Rejection: รอ Price Action ปฏิเสธ Order Block (เช่น เกิด Pin Bar, Engulfing)
- Break of Structure: รอให้ราคา Break โครงสร้างย่อยๆ ใน TF ที่เล็กกว่า (เช่น 1m, 5m) หลังจากที่ทดสอบ Order Block
- Money Flow: ดู Money Flow ให้เป็นสีแดง
- ตั้ง Stop Loss: เหนือ Order Block
- ตั้ง Take Profit: แนวรับถัดไป (เช่น Low ล่าสุด) หรือ Order Block ขาขึ้น (Bullish Order Block) ใน TF ที่ใหญ่กว่า
คำแนะนำ:
- ความขัดแย้งของ Timeframes: มีอยู่ แต่แนวโน้มระยะกลาง-สั้น เป็นลบ
- Money Flow: เป็นลบในทุก Timeframes
- Trend Strength: เริ่มมี Divergence ใน TF15
- Order Block TF Day: หลุด Order Block ขาขึ้นแล้ว
- ถ้าไม่แน่ใจ อย่าเพิ่งเข้าเทรด
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-
 @ 94a6a78a:0ddf320e
2025-02-19 21:10:15
@ 94a6a78a:0ddf320e
2025-02-19 21:10:15Nostr is a revolutionary protocol that enables decentralized, censorship-resistant communication. Unlike traditional social networks controlled by corporations, Nostr operates without central servers or gatekeepers. This openness makes it incredibly powerful—but also means its success depends entirely on users, developers, and relay operators.
If you believe in free speech, decentralization, and an open internet, there are many ways to support and strengthen the Nostr ecosystem. Whether you're a casual user, a developer, or someone looking to contribute financially, every effort helps build a more robust network.
Here’s how you can get involved and make a difference.
1️⃣ Use Nostr Daily
The simplest and most effective way to contribute to Nostr is by using it regularly. The more active users, the stronger and more valuable the network becomes.
✅ Post, comment, and zap (send micro-payments via Bitcoin’s Lightning Network) to keep conversations flowing.\ ✅ Engage with new users and help them understand how Nostr works.\ ✅ Try different Nostr clients like Damus, Amethyst, Snort, or Primal and provide feedback to improve the experience.
Your activity keeps the network alive and helps encourage more developers and relay operators to invest in the ecosystem.
2️⃣ Run Your Own Nostr Relay
Relays are the backbone of Nostr, responsible for distributing messages across the network. The more independent relays exist, the stronger and more censorship-resistant Nostr becomes.
✅ Set up your own relay to help decentralize the network further.\ ✅ Experiment with relay configurations and different performance optimizations.\ ✅ Offer public or private relay services to users looking for high-quality infrastructure.
If you're not technical, you can still support relay operators by subscribing to a paid relay or donating to open-source relay projects.
3️⃣ Support Paid Relays & Infrastructure
Free relays have helped Nostr grow, but they struggle with spam, slow speeds, and sustainability issues. Paid relays help fund better infrastructure, faster message delivery, and a more reliable experience.
✅ Subscribe to a paid relay to help keep it running.\ ✅ Use premium services like media hosting (e.g., Azzamo Blossom) to decentralize content storage.\ ✅ Donate to relay operators who invest in long-term infrastructure.
By funding Nostr’s decentralized backbone, you help ensure its longevity and reliability.
4️⃣ Zap Developers, Creators & Builders
Many people contribute to Nostr without direct financial compensation—developers who build clients, relay operators, educators, and content creators. You can support them with zaps! ⚡
✅ Find developers working on Nostr projects and send them a zap.\ ✅ Support content creators and educators who spread awareness about Nostr.\ ✅ Encourage builders by donating to open-source projects.
Micro-payments via the Lightning Network make it easy to directly support the people who make Nostr better.
5️⃣ Develop New Nostr Apps & Tools
If you're a developer, you can build on Nostr’s open protocol to create new apps, bots, or tools. Nostr is permissionless, meaning anyone can develop for it.
✅ Create new Nostr clients with unique features and user experiences.\ ✅ Build bots or automation tools that improve engagement and usability.\ ✅ Experiment with decentralized identity, authentication, and encryption to make Nostr even stronger.
With no corporate gatekeepers, your projects can help shape the future of decentralized social media.
6️⃣ Promote & Educate Others About Nostr
Adoption grows when more people understand and use Nostr. You can help by spreading awareness and creating educational content.
✅ Write blogs, guides, and tutorials explaining how to use Nostr.\ ✅ Make videos or social media posts introducing new users to the protocol.\ ✅ Host discussions, Twitter Spaces, or workshops to onboard more people.
The more people understand and trust Nostr, the stronger the ecosystem becomes.
7️⃣ Support Open-Source Nostr Projects
Many Nostr tools and clients are built by volunteers, and open-source projects thrive on community support.
✅ Contribute code to existing Nostr projects on GitHub.\ ✅ Report bugs and suggest features to improve Nostr clients.\ ✅ Donate to developers who keep Nostr free and open for everyone.
If you're not a developer, you can still help with testing, translations, and documentation to make projects more accessible.
🚀 Every Contribution Strengthens Nostr
Whether you:
✔️ Post and engage daily\ ✔️ Zap creators and developers\ ✔️ Run or support relays\ ✔️ Build new apps and tools\ ✔️ Educate and onboard new users
Every action helps make Nostr more resilient, decentralized, and unstoppable.
Nostr isn’t just another social network—it’s a movement toward a free and open internet. If you believe in digital freedom, privacy, and decentralization, now is the time to get involved.
-
 @ 5de23b9a:d83005b3
2025-02-19 03:47:19
@ 5de23b9a:d83005b3
2025-02-19 03:47:19In a digital era that is increasingly controlled by large companies, the emergence of Nostr (Notes and Other Stuff Transmitted by Relays) is a breath of fresh air for those who crave freedom of expression.
Nostr is a cryptography-based protocol that allows users to send and receive messages through a relay network. Unlike conventional social media such as Twitter or Facebook
1.Full Decentralization: No company or government can remove or restrict content.
2.Sensor-Resistant: Information remains accessible despite blocking attempts.
3.Privacy and Security: Uses cryptography to ensure that only users who have the keys can access their messages.* **
-
 @ d360efec:14907b5f
2025-02-18 15:11:58
@ d360efec:14907b5f
2025-02-18 15:11:58ภาพรวม BTCUSDT (OKX):
Bitcoin (BTCUSDT) กำลังแสดงความผันผวนอย่างมาก โดยมีสัญญาณที่ขัดแย้งกันระหว่าง Timeframes ต่างๆ แนวโน้มระยะยาว (Day) ยังคงเป็นขาขึ้น แต่ระยะกลาง (4H) และระยะสั้น (15m) แสดงให้เห็นถึงแรงขายและการปรับฐานที่รุนแรง การวิเคราะห์นี้จะเน้นการระบุพื้นที่ที่ Smart Money อาจจะเข้าซื้อหรือขาย (Liquidity Pools) และประเมินความแข็งแกร่งของแนวโน้ม
วิเคราะห์ทีละ Timeframe:
(1) TF Day (รายวัน):
- แนวโน้ม: ขาขึ้น (Uptrend) แต่เริ่มอ่อนแรง
- SMC:
- Higher Highs (HH) และ Higher Lows (HL) เริ่มไม่ชัดเจน
- Break of Structure (BOS) ด้านบน แต่เริ่มมีการปรับฐาน
- Liquidity:
- มี Sellside Liquidity (SSL) อยู่ใต้ Lows ก่อนหน้า (บริเวณ 85,000 - 90,000)
- มี Buyside Liquidity (BSL) อยู่เหนือ High เดิม (109,998.9)
- ICT:
- ยังไม่เห็น Order Block หรือ FVG ที่ชัดเจนใน TF Day ณ ราคาปัจจุบัน
- EMA:
- ราคา หลุด EMA 50 (สีเหลือง) ลงมาแล้ว
- EMA 200 (สีขาว) เป็นแนวรับถัดไป
- Money Flow (LuxAlgo):
- แท่งสีแดงยาว แสดงถึงแรงขายที่เข้ามา
- Trend Strength (AlgoAlpha): ไม่มีในภาพ
- Volume Profile: Volume ค่อนข้างเบาบาง
- แท่งเทียน: แท่งเทียนล่าสุดเป็นสีแดง แสดงถึงแรงขาย
- แนวรับ: EMA 200, บริเวณ 85,000 - 90,000 (SSL)
- แนวต้าน: EMA 50, High เดิม
- สรุป: แนวโน้มขาขึ้นเริ่มอ่อนแรง, ราคาหลุด EMA 50, Money Flow เป็นลบ, มี SSL ด้านล่าง
(2) TF4H (4 ชั่วโมง):
- แนวโน้ม: ขาลง (Downtrend) ระยะสั้น หลังจากราคาหลุด EMA 50
- SMC:
- Lower Highs (LH) และ Lower Lows (LL)
- Break of Structure (BOS) ด้านล่าง
- Liquidity:
- มี SSL อยู่ใต้ Lows ก่อนหน้า (บริเวณ 92,000)
- มี BSL อยู่เหนือ Highs ก่อนหน้า (บริเวณ 104,000 - 108,000)
- ICT:
- Order Block: ราคาลงมาใกล้ Order Block ขาขึ้น (บริเวณแท่งเทียนสีเขียวก่อนที่จะขึ้น)
- EMA:
- ราคาอยู่ใต้ EMA 50 และ EMA 200
- Money Flow (LuxAlgo):
- สีแดงเป็นส่วนใหญ่ แสดงถึงแรงขาย
- Trend Strength (AlgoAlpha): ไม่มีในภาพ
- Volume Profile Volume ค่อนข้างเบาบาง
- แนวรับ: Order Block, บริเวณ 92,000 (SSL)
- แนวต้าน: EMA 50, EMA 200, บริเวณ Highs ก่อนหน้า
- สรุป: แนวโน้มขาลงระยะสั้น, ราคาลงมาใกล้ Order Block, Money Flow เป็นลบ
(3) TF15 (15 นาที):
- แนวโน้ม: ขาลง (Downtrend)
- SMC:
- Lower Highs (LH) และ Lower Lows (LL)
- Break of Structure (BOS) ด้านล่าง
- Liquidity:
- มี SSL อยู่ใต้ Lows ล่าสุด
- มี BSL อยู่เหนือ Highs ก่อนหน้า
- ICT:
- Order Block: ราคาลงมาใกล้ Oder Block
- EMA:
- EMA 50 และ EMA 200 เป็นแนวต้าน
- Money Flow (LuxAlgo):
- สีแดงเป็นส่วนใหญ่ แสดงถึงแรงขาย
- Trend Strength (AlgoAlpha):
- เป็นสีแดง แสดงถึงเเนวโน้มขาลง
- Volume Profile:
- Volume ค่อนข้างเบาบาง
- แนวรับ: บริเวณ Low ล่าสุด
- แนวต้าน: EMA 50, EMA 200, บริเวณ Highs ก่อนหน้า
- สรุป: แนวโน้มขาลง, แรงขายมีอิทธิพล, ใกล้แนวรับ
สรุปภาพรวมและกลยุทธ์ (BTCUSDT):
- แนวโน้มหลัก (Day): ขาขึ้น (อ่อนแรง)
- แนวโน้มรอง (4H): ขาลง (ระยะสั้น)
- แนวโน้มระยะสั้น (15m): ขาลง
- Liquidity:
- Day: SSL (85,000-90,000), BSL (เหนือ 109,998.9)
- 4H: SSL (92,000), BSL (104,000-108,000)
- 15m: SSL (ใต้ Lows), BSL (เหนือ Highs)
- Money Flow: Day เริ่มเป็นลบ, 4H เป็นลบ, 15m เป็นลบ
- Trend Strength 15 m : ขาลง
- กลยุทธ์:
- Wait & See (ดีที่สุด): รอความชัดเจน
- Short (เสี่ยง): ถ้าไม่สามารถ Breakout EMA/แนวต้านใน TF ใดๆ ได้
- ไม่แนะนำให้ Buy: จนกว่าจะมีสัญญาณกลับตัวที่ชัดเจน
คำแนะนำ:
- ความขัดแย้งของ Timeframes: ชัดเจน
- Money Flow: เป็นลบในทุก Timeframes
- ระวัง SSL: Smart Money อาจจะลากราคาลงไปกิน Stop Loss
- ถ้าไม่แน่ใจ อย่าเพิ่งเข้าเทรด
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-
 @ d360efec:14907b5f
2025-02-18 13:18:54
@ d360efec:14907b5f
2025-02-18 13:18:54นักพนันแห่งเฮรันเทล
“คณิตศาสตร์” กุญแจเวทมนตร์ นักพนัน และ นักลงทุน
ในนครเฮรันเทล นามกระฉ่อนเลื่องลือในหมู่นักเสี่ยงโชค เมื่อเอ่ยถึง “การพนัน” ภาพที่ชาวเมืองมักนึกถึงคือ “ยาจกข้างถนน”
มิใช่เรื่องแปลกประหลาดอันใด เพราะเป็นที่ร่ำลือกันว่า จ้าวแห่งหอคอยรัตติกาล ผู้คุมบ่อนพนัน มักร่ายเวทมนตร์สร้างเกมให้ตนเองได้เปรียบ เพื่อดูดกลืนเงินทองของผู้มาเยือน
ดังนั้น การที่สามัญชนจะพิชิตเกมในระยะยาว จึงเป็นดั่งเงามายาที่จับต้องมิได้
กระนั้น ยังมีตำนานกล่าวขานถึงผู้กล้า ที่สามารถสร้างชื่อจาก “เกมพนัน” เช่น
เวเนสซา รุสโซ นักเวทย์มนตร์ผู้ใช้กฎหมายแห่งแดนไกล ใช้เวลายาวนานถึงหกปี
ร่ายเวทย์สะสมทรัพย์สินกว่าร้อยล้านเหรียญทอง จากการเล่นเกมไพ่ศักดิ์สิทธิ์ “โป๊กเกอร์”
หรือแม้แต่ เอ็ดเวิร์ด โอ. ทอร์ป จอมปราชญ์ผู้สร้างกำไรถึงสามแสนหกหมื่นเหรียญทอง ภายในเจ็ดราตรี
จากการเล่นเกมไพ่มนตรา “แบล็กแจ็ก” ด้วยเงินทุนตั้งต้นเพียงสามแสนสามหมื่นเหรียญทอง คิดเป็นอัตราเวทย์ตอบแทนร้อยสิบส่วน!
เหล่าจอมยุทธ์เหล่านี้ มิได้อาศัยเพียงโชคช่วยชั่วครั้งชั่วคราวแล้วเลือนหาย
แต่พวกเขากลับสามารถร่ายเวทย์สร้างผลตอบแทนระยะยาว จนเรียกได้ว่า ใช้ “หอคอยรัตติกาล” เป็นแหล่งเสบียงเลี้ยงชีพ
โดยกุญแจเวทย์ที่บุคคลเหล่านี้ใช้ ก็คือ “คณิตศาสตร์”
เหตุใด “คณิตศาสตร์” จึงช่วยให้ผู้คนเอาชนะ “การพนัน” ได้?
และนอกจาก “การพนัน” แล้ว “คณิตศาสตร์” ยังสามารถประยุกต์ใช้กับสิ่งใดได้อีก?
นักเล่าเรื่องแห่งเฮรันเทล จักไขปริศนาให้ฟัง
เบื้องต้น ขอให้ท่านลองพิจารณาตนเอง ว่าเคยประสบพบพานเหตุการณ์เหล่านี้หรือไม่:
-
ตั้งมั่นว่า จักเสี่ยงโชคให้ได้กำไรเพียงเล็กน้อย แล้วจักหยุดพัก
-
แต่หากพลาดท่าเสียที จักจำกัดการสูญเสียให้เท่าทุนเดิมที่ตั้งไว้
-
ครั้นเมื่อเวทมนตร์เข้าข้าง ได้กำไรมาแล้ว กลับโลภโมโทสัน อยากได้เพิ่มอีกนิด จึงร่ายเวทย์ต่อ
-
ทว่ากำไรเริ่มร่อยหรอ จนเหลือเพียงทุนเดิม สุดท้ายทุนที่ตั้งไว้คราแรกก็มลายสิ้น
-
จำต้องหาเงินทองมาลงเพิ่ม หวังทวงทุนคืน และพบว่าต้องสูญเสียเงินก้อนนั้นไปในห้วงเวลาต่อมา
ลำดับเหตุการณ์ดังกล่าว เรียกได้ว่าเป็น “วงจรอุบาทว์” สำหรับนักพนันมากมายในเฮรันเทล
ปริศนาที่ตามมาก็คือ เหตุใด “วงจรอุบาทว์” นี้จึงเกิดขึ้นซ้ำแล้วซ้ำเล่า?
ส่วนหนึ่ง ย่อมเป็นเพราะอารมณ์อันแปรปรวนในการเสี่ยงโชคของแต่ละคน
แต่อีกส่วนที่สำคัญยิ่งกว่า ต้องกล่าวว่าเป็นผลจาก “กลไกต้องสาป” ของจ้าวแห่งหอคอยรัตติกาล
ซึ่งต้องกล่าวว่า เหล่าเจ้าของหอคอยรัตติกาลนั้น จักใช้หลักการทำนองเดียวกับ “สมาคมพ่อค้าผู้พิทักษ์”
คือจักเก็บเงินทองจากชนจำนวนมาก เพื่อนำมาจ่ายให้กับชนเพียงหยิบมือ
เพื่อล่อลวงให้ชนทั้งหลายเสี่ยงโชคต่อไป หรือทำให้เหล่านักพนันหวังว่า จักเป็นผู้โชคดีเฉกเช่นพวกเขาบ้าง
แม้จะมีผู้โชคดีที่สามารถได้กำไรในเบื้องต้น แต่ในบั้นปลายก็จักพ่ายแพ้อยู่ดี ซึ่งเป็นไปตาม “กฎแห่งจำนวนมหาศาล” เพราะจ้าวแห่งหอคอยรัตติกาลนั้น ได้คำนวณและออกแบบระบบเกมที่ตนเองได้เปรียบในระยะยาวแล้ว
จากตำนานนี้ ย่อมประจักษ์ชัดว่า แม้การพนันจักเป็นเรื่องของดวงชะตา
แต่ก็ถูกรังสรรค์ขึ้นจากการคำนวณทางคณิตศาสตร์
ดังนั้น หากปรารถนาจะหาหนทางเอาชนะจ้าวแห่งหอคอยรัตติกาล ก็จำต้องเข้าใจ “คณิตศาสตร์” เสียก่อน
ทีนี้ จงเงี่ยหูฟัง แล้วท่านจักได้ยินข้าไขปริศนา:
๑. ปริศนาแห่ง “กำไรคาดหวัง”
สำหรับการแสวงหา “เกมเสี่ยงทาย” ที่ควรค่าแก่การเล่น หรือการเสี่ยง
สิ่งแรกที่นักพนันพึงกระทำคือ “การประเมินกำไรคาดหวัง” หรือ “เวทคำนวณอนาคต”
“กำไรคาดหวัง” ถูกคิดค้นโดย คริสเตียน ฮอยเกนส์ นักปราชญ์เวทย์ชาวดัตช์ เพื่อประเมินว่าเกมพนันแบบใดควรค่าแก่การเล่น ซึ่งมิใช่เพียงแค่การประเมินโอกาสแห่งชัยชนะเท่านั้น แต่ต้องคิดรวมขนาดของเงินเดิมพันไปด้วย
โดยสูตรเวทย์คือ:
กำไรคาดหวัง = (เงินที่ได้ x โอกาสชนะ) + (เงินที่เสีย x โอกาสแพ้)
ดังนั้น หากปรารถนาจะสะสม “ทองคำมายา” ในระยะยาว จงเลือกเกมที่มี “กำไรคาดหวัง” เป็นบวก
แต่หากพลาดพลั้งเข้าไปเล่นเกมที่ “กำไรคาดหวัง” เป็นลบ และบังเอิญว่าโชคชะตาเล่นตลกให้ได้เงินทองมาครอง
พึงละทิ้งเกมนั้นเสียโดยพลัน เพราะท้ายที่สุดหากยังคงเล่นต่อไป ผู้อับโชคผู้นั้นก็คือตัวท่านเอง
อย่างไรก็ตาม โดยธรรมดาแล้ว “กำไรคาดหวัง” ของเกมพนันที่มีเจ้ามือมักจักติดลบ จึงเป็นเรื่องยากยิ่งที่จะเอาชนะได้ เฉกเช่นตัวอย่างที่เราเห็น คือเกมในบ่อนพนัน หรือแม้แต่ “สลากกินแบ่งรัฐบาล” ก็ล้วนเป็นเกมที่มี “กำไรคาดหวัง” ติดลบทั้งสิ้น
นอกจาก “กำไรคาดหวัง” จักถูกใช้กับการพนันได้แล้ว
หลักเวทย์ “คณิตศาสตร์” ก็ยังสามารถประยุกต์ใช้กับการลงทุนได้ไม่แตกต่างกัน
ตัวอย่างเช่น หากท่านเก็บสถิติข้อมูลการลงทุนของตนเอง
แล้วพบว่ามีเพียงสามสิบส่วนร้อยเท่านั้น ที่ท่านซื้อ “ศิลาแห่งโชค” แล้วสร้างผลตอบแทนเป็นบวก
แต่ท่านยังคงปรารถนาความสำเร็จในการลงทุน
ก็จงจำกัดการขาดทุนแต่ละคราให้น้อยเข้าไว้ เช่น -๕%
และปล่อยให้มีกำไรในแต่ละคราที่ลงทุน เช่น อย่างน้อย ๒๐%
ซึ่งจากการใช้กลยุทธ์นี้ ท่านจักมี “กำไรคาดหวัง” = (๒๐% x ๐.๓) + (-๕% x ๐.๗) = ๒.๕%
จักเห็นได้ว่า แม้ท่านจักมีจำนวนคราที่ขาดทุนบ่อยครั้ง แต่ก็ยังสามารถสร้างกำไรได้
หากคราที่กำไรนั้น สามารถทำเงินทองเป็นจำนวนมากได้
๒. ปริศนาแห่ง “การบริหารหน้าตัก” หรือ “การบริหารเงินทุน”
แม้ว่าท่านจักรับรู้ “กำไรคาดหวัง” แล้ว แต่หากท่านเผชิญหน้ากับการขาดทุนต่อเนื่องกัน ท่านก็อาจหมดเนื้อหมดตัวก่อนถึงคราที่จะกอบโกยเงินทองจากคราที่กำไร
วิธีคลายปมปริศนานี้ก็คือ การมิลงเงินทองทั้งหมดของท่านในการลงทุนเพียงคราเดียว
ซึ่งนอกจากการกระจายความเสี่ยงในการลงทุนหลาย “ศิลาแห่งโชค” หรือหลาย “เกมเสี่ยงทาย” แล้ว
ท่านอาจกำหนดขนาดของการลงทุนแต่ละคราให้มิมากเกินไป แบบง่าย ๆ เช่น มิเกิน ๑๐% ของเงินลงทุนทั้งหมด หรือท่านอาจคำนวณขนาดของการลงทุนแต่ละคราด้วยสูตรทางคณิตศาสตร์ เช่น สูตร “การขาดทุนสูงสุดที่ท่านรับได้ (Value at Risk)” หรือ สูตร “ขนาดเดิมพันที่เหมาะสม (Kelly Formula)”
๓. ปริศนาแห่ง “อคติ”
ในวงการพนัน มักมีอคติหนึ่งที่บังเกิดบ่อยครั้งกับผู้คน คือ “Gambler's Fallacy” หรือ “ความเชื่อผิด ๆ แห่งนักพนัน” ว่าหากเหตุการณ์หนึ่งบังเกิดบ่อยครั้งกว่าปรกติในช่วงเวลาหนึ่ง ๆ
เหตุการณ์นั้นจักบังเกิดบ่อยครั้งน้อยลงในอนาคต ทั้ง ๆ ที่เหตุการณ์เหล่านั้นเป็นอิสระจากกันในทางสถิติ
ยกตัวอย่างเช่น หากโยนเหรียญมนตราออกหัวไปแล้วสามครา ในคราที่สี่ หลายคนอาจคิดว่าโอกาสออกก้อยมากกว่าหัว แม้ว่าการโยนเหรียญแต่ละคราจะมิได้ส่งผลอันใดต่อกันเลย (จะโยนกี่ครา โอกาสหัวหรือก้อย ก็คือ ๕๐:๕๐ อยู่ยั่งยืน)
หรือแม้กระทั่ง “สลากกินแบ่งรัฐบาล” มีหลายคนที่ซื้อเลขซ้ำกัน เพื่อหวังว่าจะถูกในงวดต่อ ๆ ไป
ในวงการการลงทุน ก็มีลักษณะที่คล้ายคลึงกัน เช่น หาก “ศิลาแห่งโชค A” ราคาตกต่ำลงมาห้าครา บางคนอาจคิดว่าในคราที่หก ราคาของมันจักต้องเด้งขึ้นมา ซึ่งในความเป็นจริง หาได้เป็นเช่นนั้นเสมอไป
จักเห็นได้ว่า แท้จริงแล้ว ไม่ว่าจักเป็น “เกมเสี่ยงทายแห่งโชคชะตา” หรือ “การผจญภัยในตลาดทุน”
หากท่านมีความเข้าใจ และนำ “คณิตศาสตร์” เข้ามาเป็นรากฐาน
มันก็อาจนำพาตัวท่านเอง ไปสู่จุดที่ได้เปรียบในเกมนั้น ได้เฉกเช่นกัน..
สูตรเวทย์มนตร์ที่ปรากฏในตำนาน:
- กำไรคาดหวัง = (เงินที่ได้ x โอกาสชนะ) + (เงินที่เสีย x โอกาสแพ้)
คำเตือนจากนักเล่าเรื่องแห่งเฮรันเทล:
"พึงระลึกไว้เสมอว่า โชคชะตาเป็นสิ่งที่คาดเดาได้ยาก แม้เวทมนตร์คณิตศาสตร์จักช่วยนำทาง แต่ท้ายที่สุดแล้ว ความสำเร็จยังคงขึ้นอยู่กับการตัดสินใจและสติปัญญาของท่านเอง"
หวังว่าตำนานบทนี้จักเป็นประโยชน์แก่ท่านนะคะ
-
-
 @ d360efec:14907b5f
2025-02-17 12:20:25
@ d360efec:14907b5f
2025-02-17 12:20:253 พฤติกรรมที่เป็นอุปสรรคต่อการทำกำไรของนักลงทุนส่วนใหญ่
นักลงทุนจำนวนมากต้องการที่จะประสบความสำเร็จในตลาดหุ้นและสร้างผลกำไรที่สม่ำเสมอ แต่หลายครั้งที่พวกเขากลับพบว่าตัวเองต้องเผชิญกับอุปสรรคที่ทำให้ไม่สามารถบรรลุเป้าหมายนั้นได้ ช่อง Zyo / เซียว จับอิดนึ้ง ได้นำเสนอ 3 พฤติกรรมที่เป็นอุปสรรคสำคัญต่อนักลงทุนส่วนใหญ่ ซึ่งหากนักลงทุนสามารถหลีกเลี่ยงพฤติกรรมเหล่านี้ได้ ก็จะมีโอกาสในการสร้างผลกำไรที่สม่ำเสมอมากยิ่งขึ้น
-
การซื้อขายตามอารมณ์: ตลาดหุ้นมีความผันผวนและเต็มไปด้วยข่าวสารมากมาย นักลงทุนที่ซื้อขายตามอารมณ์มักจะตัดสินใจโดยใช้อารมณ์เป็นหลัก ไม่ว่าจะเป็นความโลภเมื่อเห็นราคาหุ้นขึ้น หรือความกลัวเมื่อราคาหุ้นตก การตัดสินใจที่ไม่ได้อยู่บนพื้นฐานของข้อมูลและการวิเคราะห์อย่างรอบคอบ มักนำไปสู่การตัดสินใจที่ผิดพลาดและขาดทุนในที่สุด
-
การไม่ยอมรับความเสี่ยง: การลงทุนในตลาดหุ้นมีความเสี่ยง นักลงทุนที่ไม่ยอมรับความเสี่ยงมักจะพลาดโอกาสในการลงทุนในสินทรัพย์ที่ให้ผลตอบแทนสูง หรือในทางกลับกัน พวกเขาอาจจะหลีกเลี่ยงการตัดขาดทุนเมื่อการลงทุนไม่เป็นไปตามที่คาดหวัง การไม่ยอมรับความเสี่ยงและไม่บริหารความเสี่ยงอย่างเหมาะสม จะทำให้พอร์ตการลงทุนไม่เติบโตเท่าที่ควร หรืออาจจะเผชิญกับความเสียหายที่ใหญ่หลวงได้
-
การขาดความรู้และความเข้าใจ: ตลาดหุ้นเป็นเรื่องที่ซับซ้อนและเปลี่ยนแปลงอยู่เสมอ นักลงทุนที่ขาดความรู้และความเข้าใจในเรื่องการลงทุนอย่างเพียงพอ มักจะลงทุนโดยไม่มีหลักการหรือไม่สามารถวิเคราะห์สถานการณ์ได้อย่างถูกต้อง การลงทุนโดยปราศจากความรู้และความเข้าใจที่ถูกต้อง ก็เหมือนกับการเดินอยู่ในความมืด ซึ่งโอกาสที่จะประสบความสำเร็จนั้นเป็นไปได้ยาก
บทสรุป
3 พฤติกรรมที่กล่าวมาข้างต้นเป็นเพียงส่วนหนึ่งของอุปสรรคที่นักลงทุนส่วนใหญ่ต้องเผชิญ หากนักลงทุนต้องการที่จะประสบความสำเร็จในการลงทุนอย่างยั่งยืน พวกเขาจำเป็นต้องตระหนักถึงพฤติกรรมเหล่านี้และพยายามปรับปรุงตนเองอย่างต่อเนื่อง การศึกษาหาความรู้เพิ่มเติม การวางแผนการลงทุนอย่างรอบคอบ และการควบคุมอารมณ์ จะเป็นกุญแจสำคัญที่นำไปสู่การสร้างผลกำไรที่สม่ำเสมอในตลาดหุ้นได้ แน่นอนค่ะ ฟังคลิปแล้ว และสรุปบทความเป็นภาษาไทยให้คุณแล้วค่ะ
บทความ: 3 พฤติกรรมที่เป็นอุปสรรคต่อการทำกำไรสม่ำเสมอของนักลงทุนส่วนใหญ่
บทความนี้สรุปแนวคิดจากคลิปวิดีโอที่วิเคราะห์พฤติกรรมของนักลงทุนส่วนใหญ่ โดยอ้างอิงจากการสำรวจบัญชีซื้อขายหุ้นกว่า 77,000 บัญชีในช่วงปี 1990-1996 พบว่ามี 3 พฤติกรรมหลักที่เป็นอุปสรรคสำคัญต่อการสร้างผลกำไรที่สม่ำเสมอในการลงทุน
3 พฤติกรรมที่เป็นอุปสรรคต่อการทำกำไร:
-
ปล่อยให้ขาดทุน แต่รีบขายกำไร: นักลงทุนส่วนใหญ่มักจะถือหุ้นที่กำลังขาดทุนต่อไปเรื่อย ๆ เพราะไม่อยากยอมรับว่าตัดสินใจผิดพลาด ในทางกลับกัน เมื่อหุ้นเริ่มมีกำไรเพียงเล็กน้อย กลับรีบขายออกไปเพราะกลัวกำไรจะหายไป พฤติกรรมนี้เป็นผลจากธรรมชาติของมนุษย์ที่เรียกว่า "Loser Aversion" หรือการหลีกเลี่ยงความเจ็บปวดจากการขาดทุนมากกว่าความสุขจากการได้กำไร
-
ถัวเฉลี่ยขาลง มากกว่าพีระมิดขาขึ้น: นักลงทุนจำนวนมากเลือกที่จะซื้อหุ้นที่ราคาลดลง (ถัวเฉลี่ยขาลง) โดยหวังว่าจะได้ต้นทุนที่ต่ำลงและรอให้ราคาหุ้นกลับมา แต่ในความเป็นจริง หุ้นที่อยู่ในแนวโน้มขาลงก็มีโอกาสที่จะลงต่อไปเรื่อย ๆ การถัวเฉลี่ยขาลงจึงเป็นการเพิ่มความเสี่ยง ในขณะที่การ "พีระมิดขาขึ้น" หรือการซื้อหุ้นเพิ่มเมื่อราคาปรับตัวสูงขึ้น เป็นการลงทุนในหุ้นที่กำลังมีแนวโน้มที่ดีและมีโอกาสสร้างกำไรมากกว่า
-
รีบขายกำไรเล็กน้อย แต่ไม่ยอมขายเมื่อขาดทุนเล็กน้อย: พฤติกรรมนี้ต่อเนื่องจากข้อแรก คือเมื่อได้กำไรเพียงเล็กน้อย นักลงทุนมักจะรีบขายเพื่อ "ล็อกกำไร" แต่เมื่อขาดทุนเล็กน้อย กลับไม่ยอมขายเพราะหวังว่าราคาจะกลับมา ทำให้สุดท้ายกลายเป็น "กำไรน้อย รีบขาย ขาดทุน เก็บไว้" ซึ่งส่งผลเสียต่อพอร์ตการลงทุนในระยะยาว
คำแนะนำเพื่อปรับปรุงพฤติกรรมการลงทุน:
- ฝึก "Cut Loss Short, Let Profit Run": ยอมตัดขาดทุนเมื่อหุ้นไม่เป็นไปตามแผน เพื่อจำกัดความเสียหาย และปล่อยให้หุ้นที่กำลังทำกำไรทำงานไป เพื่อเพิ่มโอกาสในการทำกำไรที่มากขึ้น
- อย่าถัวเฉลี่ยขาลงโดยไม่มีเหตุผล: พิจารณาแนวโน้มของหุ้นและปัจจัยพื้นฐานก่อนตัดสินใจถัวเฉลี่ยขาลง หากไม่มีเหตุผลที่ชัดเจน การถัวเฉลี่ยขาลงอาจเป็นการเพิ่มความเสี่ยงโดยไม่จำเป็น
- บริหารความเสี่ยงและ Money Management อย่างเหมาะสม: กำหนด stop loss ที่ชัดเจน และบริหารจัดการเงินทุนให้เหมาะสมกับความเสี่ยงที่รับได้
- เรียนรู้และพัฒนาระบบเทรดของตัวเองอย่างต่อเนื่อง: ทำความเข้าใจกลยุทธ์การเทรดของตนเอง และปรับปรุงพัฒนาอย่างสม่ำเสมอ
- มี Mindset ที่ถูกต้องสำหรับการเทรด: เข้าใจว่าการเทรดสวนทางกับธรรมชาติของมนุษย์ ต้องฝึกฝนและสร้างนิสัยที่ถูกต้องเพื่อเอาชนะอุปสรรคทางจิตวิทยา
สรุป:
การลงทุนและการเทรดหุ้นเป็นเกมที่ "ผิดธรรมชาติ" ของมนุษย์ การเอาชนะตลาดหุ้นได้จึงต้องอาศัยการฝึกฝนและปรับเปลี่ยนพฤติกรรมให้สวนทางกับธรรมชาติเดิม ๆ โดยการตระหนักถึง 3 พฤติกรรมที่เป็นอุปสรรค และนำคำแนะนำไปปรับใช้ จะช่วยให้นักลงทุนสามารถพัฒนาไปสู่การสร้างผลกำไรที่สม่ำเสมอและยั่งยืนได้ในระยะยาว
-
-
 @ d360efec:14907b5f
2025-02-17 08:49:15
@ d360efec:14907b5f
2025-02-17 08:49:15ภาพรวม BTCUSDT (OKX):
Bitcoin ยังคงอยู่ในแนวโน้มขาขึ้นระยะยาว แต่ระยะสั้นมีความผันผวนและมีการปรับฐานลงมา การวิเคราะห์ครั้งนี้จะเน้นการระบุพื้นที่ที่ Smart Money (หรือ "เจ้ามือ") อาจจะเข้าซื้อหรือขาย เพื่อให้เราสามารถวางแผนการเทรดได้อย่างมีประสิทธิภาพ
วิเคราะห์ทีละ Timeframe:
(1) TF Day (รายวัน):
- แนวโน้ม: ขาขึ้น (Uptrend)
- SMC:
- Higher Highs (HH) และ Higher Lows (HL) ต่อเนื่อง
- Break of Structure (BOS) ด้านบน
- ยังไม่มีสัญญาณการกลับตัวเป็นขาลง
- ICT:
- ยังไม่เห็น Order Block หรือ FVG ที่ชัดเจนใน TF Day ณ ราคาปัจจุบัน
- EMA:
- ราคาอยู่เหนือ EMA 50 (สีเหลือง) และ EMA 200 (สีขาว) (Golden Cross)
- Money Flow (LuxAlgo):
- สีเขียวเป็นส่วนใหญ่ แสดงถึงแรงซื้อ
- Volume Profile:
- Volume หนาแน่นที่บริเวณต่ำกว่าราคาปัจจุบัน
- แท่งเทียน:
- แท่งเทียนล่าสุดเป็นสีแดง แสดงถึงแรงขาย แต่ไส้เทียนยาว แสดงว่ามีแรงซื้อกลับ
- แนวรับ: EMA 50, EMA 200, บริเวณ Volume Profile หนาแน่น
- แนวต้าน: High เดิม
- สรุป: แนวโน้มหลักยังเป็นขาขึ้น Buy on Dip
(2) TF4H (4 ชั่วโมง):
- แนวโน้ม: ขาขึ้น (พักตัว)
- SMC:
- HH และ HL
- BOS ด้านบน
- ราคาหลุด EMA 50
- ICT:
- Fair Value Gap (FVG): สังเกตเห็น FVG เล็กๆ ที่เกิดขึ้นก่อนหน้านี้ (บริเวณที่ราคาเคยพุ่งขึ้นอย่างรวดเร็ว) อาจเป็นเป้าหมายของการ Pullback
- Order Block: ราคาปัจจุบันกำลังทดสอบ Order Block (บริเวณแท่งเทียนสีแดงแท่งใหญ่ก่อนที่จะขึ้น) เป็นจุดที่น่าสนใจมาก
- EMA:
- ราคาหลุด EMA 50
- EMA 200 เป็นแนวรับถัดไป
- Money Flow (LuxAlgo):
- เขียวและแดงผสมกัน, แดงเริ่มมากขึ้น
- Volume Profile:
- Volume profile ค่อนข้างสูง
- แนวรับ: EMA 200, Order Block, บริเวณ Volume Profile
- แนวต้าน: EMA 50, High เดิม
- สรุป: แนวโน้มขาขึ้นพักตัว, ทดสอบ Order Block, Money Flow เริ่มเป็นลบ
(3) TF15 (15 นาที):
- แนวโน้ม: ขาลง (Downtrend) ระยะสั้น แต่เริ่มมีสัญญาณการฟื้นตัว
- SMC:
- Lower Highs (LH) และ Lower Lows (LL) แต่เริ่มเห็น Higher Low
- BOS ด้านล่าง
- เริ่มมีสัญญาณการ Breakout EMA 50/200
- ICT:
- ราคาเพิ่ง Breakout Order Block ขาลง (แต่ต้องรอดูว่าจะยืนได้หรือไม่)
- EMA:
- EMA 50/200 เพิ่งจะตัดกันแบบ Golden Cross
- Money Flow (LuxAlgo):
- เริ่มมีแท่งสีเขียวปรากฏขึ้น
- Volume Profile:
- แนวรับ: บริเวณ Low ล่าสุด
- แนวต้าน: EMA50/200
- สรุป: เริ่มมีสัญญาณการฟื้นตัว แต่ยังต้องระวัง
สรุปภาพรวมและกลยุทธ์ (BTCUSDT):
- แนวโน้มหลัก (Day): ขาขึ้น
- แนวโน้มรอง (4H): ขาขึ้น (พักตัว), ทดสอบ Order Block
- แนวโน้มระยะสั้น (15m): เริ่มมีสัญญาณการฟื้นตัว
- Money Flow: Day เป็นบวก, 4H เริ่มเป็นลบ, 15m เริ่มเป็นบวก
- กลยุทธ์:
- Wait & See: รอการยืนยันการ Breakout EMA 50/200 ใน TF15m
- Buy (เสี่ยง): เฉพาะเมื่อราคา Breakout EMA 50/200 ใน TF 15 ได้อย่างแข็งแกร่ง
- Short (เสี่ยง): ถ้า Order Block ใน TF4H รับไม่อยู่ และ TF15 ยังคงเป็นขาลง
คำแนะนำ:
- Order Block: ให้ความสำคัญกับ Order Block ใน TF4H
- FVG: สังเกต FVG ใน TF4H
- ความขัดแย้งของ Timeframes: เริ่มลดลง (15m เริ่มมีสัญญาณบวก)
- จับตาดู TF15 อย่างใกล้ชิด
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-
 @ 42342239:1d80db24
2025-02-16 08:39:59
@ 42342239:1d80db24
2025-02-16 08:39:59Almost 150 years ago, the British newspaper editor William Thomas Stead wrote that "the editorial pen is a sceptre of power, compared with which the sceptre of many a monarch is but a gilded lath". He had begun to regard journalism as something more than just conveying information - the journalist or editor could become a ruler.
Times had certainly changed compared to a few hundred years earlier. Before Gutenberg's invention of the printing press, it was mainly the church that controlled the dissemination of information in Europe, but when Stead put pen to paper, this control had shifted to newspapers, schools, and universities. Eventually, technologies like radio and TV entered the scene, but the power dynamics remained asymmetrical - only a few could send information to the many.
However, with the emergence of the internet, and especially with the spread of social media, a significant change followed. Instead of only a few being able to send information to the many, many could send to many. Almost anyone could now create their own newspaper, radio, or TV channel. The power over information dissemination was decentralised.
Ten years ago, Roberta Alenius, who was then press secretary for Sweden's Prime Minister Fredrik Reinfeldt of the Moderate Party, shared her experiences with Social Democratic and Moderate Party internet activists on social media. She reported that social media played a significant role in how news "comes out" and is shaped, and that journalism was now downstream of social media. Five years later, NATO's then-Secretary-General Jens Stoltenberg said that "NATO must be prepared for both conventional and hybrid threats: from tanks to tweets." This finally underscores the importance of social media.
Elon Musk, who took over X (formerly Twitter) in 2022, has claimed that "it's absolutely fundamental and transformative that the people actually get to decide the news and narrative and what's important," and that citizen journalism is the future.
While his platform allows most expressions - for better or worse - the reach of messages is instead limited ("freedom of speech does not mean freedom of reach "). X has also opened its recommendation algorithm to the outside world by making it open-source. Although this is a welcome step, the fact remains that it's impossible to know which code is actually used and what adjustments are made by humans or algorithms.
William Thomas Stead's "sceptre of power", which has wandered from the church to newspaper and TV editorial offices, and now to citizens according to Elon Musk, risks being transferred to algorithms' opaque methods?
Instead of talking about "toxic algorithms" and TikTok bans, like the so many do today, we should ask ourselves more fundamental questions. What happens when algorithms are no longer objective (how can they ever be?), but instead become tools for shaping our reality? Perhaps our greatest challenge today is not deciding who should govern the information landscape, but instead recognising that no one is up to the task - not even well-ventilated computers.
-
 @ 9e69e420:d12360c2
2025-02-15 20:24:09
@ 9e69e420:d12360c2
2025-02-15 20:24:09Ukraine's President Volodymyr Zelensky called for an "army of Europe" to defend against Russian threats, emphasizing that the US may not continue its traditional support for Europe. Speaking at the Munich Security Conference, he warned against peace deals made without Ukraine's involvement.
US Vice President JD Vance echoed this sentiment, urging Europe to enhance its defense efforts.
Zelensky stated, "I really believe the time has come - the armed forces of Europe must be created." He highlighted changing dynamics in US-Europe relations and noted that "the old days are over" regarding American support.
Despite discussions around NATO, Zelensky stated he wouldn't rule out NATO membership for Ukraine.
-
 @ fd208ee8:0fd927c1
2025-02-15 07:37:01
@ fd208ee8:0fd927c1
2025-02-15 07:37:01E-cash are coupons or tokens for Bitcoin, or Bitcoin debt notes that the mint issues. The e-cash states, essentially, "IoU 2900 sats".
They're redeemable for Bitcoin on Lightning (hard money), and therefore can be used as cash (softer money), so long as the mint has a good reputation. That means that they're less fungible than Lightning because the e-cash from one mint can be more or less valuable than the e-cash from another. If a mint is buggy, offline, or disappears, then the e-cash is unreedemable.
It also means that e-cash is more anonymous than Lightning, and that the sender and receiver's wallets don't need to be online, to transact. Nutzaps now add the possibility of parking transactions one level farther out, on a relay. The same relays that cannot keep npub profiles and follow lists consistent will now do monetary transactions.
What we then have is * a transaction on a relay that triggers * a transaction on a mint that triggers * a transaction on Lightning that triggers * a transaction on Bitcoin.
Which means that every relay that stores the nuts is part of a wildcat banking system. Which is fine, but relay operators should consider whether they wish to carry the associated risks and liabilities. They should also be aware that they should implement the appropriate features in their relay, such as expiration tags (nuts rot after 2 weeks), and to make sure that only expired nuts are deleted.
There will be plenty of specialized relays for this, so don't feel pressured to join in, and research the topic carefully, for yourself.
https://github.com/nostr-protocol/nips/blob/master/60.md https://github.com/nostr-protocol/nips/blob/master/61.md
-
 @ 0fa80bd3:ea7325de
2025-02-14 23:24:37
@ 0fa80bd3:ea7325de
2025-02-14 23:24:37intro
The Russian state made me a Bitcoiner. In 1991, it devalued my grandmother's hard-earned savings. She worked tirelessly in the kitchen of a dining car on the Moscow–Warsaw route. Everything she had saved for my sister and me to attend university vanished overnight. This story is similar to what many experienced, including Wences Casares. The pain and injustice of that time became my first lessons about the fragility of systems and the value of genuine, incorruptible assets, forever changing my perception of money and my trust in government promises.
In 2014, I was living in Moscow, running a trading business, and frequently traveling to China. One day, I learned about the Cypriot banking crisis and the possibility of moving money through some strange thing called Bitcoin. At the time, I didn’t give it much thought. Returning to the idea six months later, as a business-oriented geek, I eagerly began studying the topic and soon dove into it seriously.
I spent half a year reading articles on a local online journal, BitNovosti, actively participating in discussions, and eventually joined the editorial team as a translator. That’s how I learned about whitepapers, decentralization, mining, cryptographic keys, and colored coins. About Satoshi Nakamoto, Silk Road, Mt. Gox, and BitcoinTalk. Over time, I befriended the journal’s owner and, leveraging my management experience, later became an editor. I was drawn to the crypto-anarchist stance and commitment to decentralization principles. We wrote about the economic, historical, and social preconditions for Bitcoin’s emergence, and it was during this time that I fully embraced the idea.
It got to the point where I sold my apartment and, during the market's downturn, bought 50 bitcoins, just after the peak price of $1,200 per coin. That marked the beginning of my first crypto winter. As an editor, I organized workflows, managed translators, developed a YouTube channel, and attended conferences in Russia and Ukraine. That’s how I learned about Wences Casares and even wrote a piece about him. I also met Mikhail Chobanyan (Ukrainian exchange Kuna), Alexander Ivanov (Waves project), Konstantin Lomashuk (Lido project), and, of course, Vitalik Buterin. It was a time of complete immersion, 24/7, and boundless hope.
After moving to the United States, I expected the industry to grow rapidly, attended events, but the introduction of BitLicense froze the industry for eight years. By 2017, it became clear that the industry was shifting toward gambling and creating tokens for the sake of tokens. I dismissed this idea as unsustainable. Then came a new crypto spring with the hype around beautiful NFTs – CryptoPunks and apes.
I made another attempt – we worked on a series called Digital Nomad Country Club, aimed at creating a global project. The proceeds from selling images were intended to fund the development of business tools for people worldwide. However, internal disagreements within the team prevented us from completing the project.
With Trump’s arrival in 2025, hope was reignited. I decided that it was time to create a project that society desperately needed. As someone passionate about history, I understood that destroying what exists was not the solution, but leaving everything as it was also felt unacceptable. You can’t destroy the system, as the fiery crypto-anarchist voices claimed.
With an analytical mindset (IQ 130) and a deep understanding of the freest societies, I realized what was missing—not only in Russia or the United States but globally—a Bitcoin-native system for tracking debts and financial interactions. This could return control of money to ordinary people and create horizontal connections parallel to state systems. My goal was to create, if not a Bitcoin killer app, then at least to lay its foundation.
At the inauguration event in New York, I rediscovered the Nostr project. I realized it was not only technologically simple and already quite popular but also perfectly aligned with my vision. For the past month and a half, using insights and experience gained since 2014, I’ve been working full-time on this project.
-
 @ 9e69e420:d12360c2
2025-02-14 18:07:10
@ 9e69e420:d12360c2
2025-02-14 18:07:10Vice President J.D. Vance addressed the Munich Security Conference, criticizing European leaders for undermining free speech and traditional values. He claimed that the biggest threat to Europe is not from external enemies but from internal challenges. Vance condemned the arrest of a British man for praying near an abortion clinic and accused European politicians of censorship.
He urged leaders to combat illegal immigration and questioned their democratic practices. “There is a new sheriff in town,” he said, referring to President Trump. Vance's remarks were unexpected, as many anticipated discussions on security or Ukraine. His speech emphasized the need for Europe to share the defense burden to ensure stability and security.
-
 @ 9e69e420:d12360c2
2025-02-14 15:14:34
@ 9e69e420:d12360c2
2025-02-14 15:14:34A Russian drone attack has struck the radiation shelter at Chernobyl, according to Ukrainian President Volodymyr Zelensky. The strike caused a fire, but it has since been extinguished, and radiation levels remain stable. The International Atomic Energy Agency (IAEA) confirmed that no casualties occurred and that monitoring continues.
Rafael Mariano Grossi, IAEA's director general, emphasized the need for caution. Chernobyl, site of the 1986 nuclear disaster, contains a protective shield costing $1.6 billion. Disaster prevention remains a priority as the conflict unfolds.
The incident occurred shortly before the meeting of world powers at the Munich Security Conference in Germany.
-
 @ b2caa9b3:9eab0fb5
2025-02-14 13:55:53
@ b2caa9b3:9eab0fb5
2025-02-14 13:55:53After spending two weeks in Arusha, it was time to move on. My next stop was Dodoma. I walked to the bus station in the center of Arusha to check ticket prices, but I disliked the chaotic atmosphere — people approached me nonstop, trying to sell me tickets to destinations I had no interest in. Instead, I went to the Shabiby office, a reputed bus company, and secured a ticket for 29,000 TZS. The bus was scheduled to leave at 10 A.M. the next day, giving me time to prepare.
 Photo above: a stop between Arusha and Dodoma.
Photo above: a stop between Arusha and Dodoma.I returned to my hostel, packed my bag, and picked up snacks and water from Shoppers Supermarket, knowing that Tanzanian bus rides tend to take longer than expected. The 80-kilometer journey from Moshi to Arusha had taken me up to three hours, so I expected the longer trip to Dodoma to stretch beyond the promised eight hours.
The Journey to Dodoma
The bus ride was predictably long, making frequent stops along the way. Upon arrival in Dodoma, the bus meandered through the city, dropping off passengers. My booked accommodation was just under two kilometers from the final stop, so I decided to walk, relying on Google Maps to guide me.
 Photo above: in Dodoma.
Photo above: in Dodoma.When I arrived at what was supposed to be my lodging, I was skeptical. The house lacked a sign, and an elderly woman was doing laundry in the yard. When I asked if this was the right place, she called a younger woman who spoke English and welcomed me inside. The accommodation was a full apartment, complete with a kitchen, but not cheap. Later in the evening, I attempted to shower, only to discover there was no running water. I resorted to a bucket shower, but the cramped bathroom caused water to spill into the apartment.
 Photo above: the Baobab Café in Dodoma.
Photo above: the Baobab Café in Dodoma.Exploring Dodoma
The next day, I set out to explore Dodoma. I passed a cozy café and an old-looking church, which I later learned was not as ancient as it seemed. Strolling down a lively shopping district, I admired the small stores lining the streets. Eventually, I settled at the café I had spotted earlier, enjoying a simple dinner of bread and tomato salad.
 Photo above: the church in Dodoma.
Photo above: the church in Dodoma.Originally, I had planned to stay for just one night, but the city intrigued me, and I extended my stay. This meant I had to book my next bus ticket and gather supplies. Using the Bolt app, I ordered a TukTuk to take me to the Shabiby bus terminal. The ride cost 2,000 TZS — without Bolt, I would have been charged significantly more. I bought my ticket to Mbeya for 40,000 TZS, with a departure time of 5:30 A.M.
That night, I packed my bags and went to bed early, knowing I had an early start ahead.
The Departure to Mbeya
Waking up at 3:30 A.M., I hurriedly took another bucket shower — still no running water. I initially planned to order a TukTuk, but the Bolt app showed no available drivers. With the bus station only a 13-minute walk away, I set out on foot. Along the way, I stepped into a water hole, soaking myself up to my knees. Street vendors persistently offered me motorcycle rides, but I ignored them and continued walking.
 Photo above: in Dodoma.
Photo above: in Dodoma.Arriving at the bus station, I saw the previous bus to Mbeya departing. My gut told me something was wrong. Sure enough, my bus was delayed by almost an hour. Finally, it arrived, and I boarded, relieved that I hadn’t missed it after all.
A Long Ride to Mbeya
The previous day, I had suffered from severe diarrhea. Fortunately, a local pharmacy in Dodoma provided me with pills that helped stabilize my system. I also continued taking my daily dose of Doxycycline as a malaria precaution.
 Photo above: shopping street in Dodoma.
Photo above: shopping street in Dodoma.This time, I had a window seat with no one beside me, allowing me to place my backpack on the empty seat. As we traveled, I watched the Tanzanian landscape unfold. At one point, the bus crossed a dam, likely a reservoir, before being stopped by police. A policeman entered, checked my passport, and inquired about my destination. When I mentioned Mbeya, he ask me where after, and I told him to Lusaka. Then he asked if it was in Zambia, returned my passport, and he let us continue.
 Photo above: the Baobab Café in Dodoma.
Photo above: the Baobab Café in Dodoma.My host in Mbeya had instructed me to get off at Nane Nane Stand. Upon arrival, I searched for a TukTuk. Without internet access, I had to negotiate fares blindly. After rejecting overpriced offers, I managed to bargain a price of 5,000 TZS for the short ride to my accommodation, what was a bit high for a Tuktuk.
Mbeya and the Journey to the Border
Initially planning to stay two nights, exhaustion led me to extend for an extra night. The hostel was beautiful and clean but, yet again, had no running water. However, this time, the host kindly boiled water for me, allowing me to take a warm bucket shower.
 Photo above: on the way to the Supermarket in Dodoma.
Photo above: on the way to the Supermarket in Dodoma.On my final day in Mbeya, I explored the city, visiting a new children's hospital and an old church. Tuktuk drivers repeatedly tried to overcharge me, but I insisted on the standard 800 TZS fare for public transport.
 Photo above: on the way to the Supermarket in Dodoma.
Photo above: on the way to the Supermarket in Dodoma.The following morning, after a quick breakfast, I set off for the bus station with a fellow traveler I met at the hostel. Together, we took a bus to Tunduma for 5,000 TZS each. From there, a TukTuk ride to the border cost another 5,000 TZS.
Crossing into Zambia
The border crossing was straightforward for me — I received a free 30-day visa for Zambia. My Russian travel companion, however, needed a visa on arrival, payable in cash and only in USD. The immigration officer arranged a taxi to take us to an ATM, but the only available bank, Absa, charged exorbitant fees. Fortunately, we later found a Zanaco ATM in Nakonde that had no fees.
 Photo above: between Dodoma and Mbeya.
Photo above: between Dodoma and Mbeya.Once we had the necessary cash, we returned to the Border immigration, paid for the visa, and proceeded into Zambia. We walked to town, grabbed some food, and checked into Shalom Hotel. It was cheap, costing only 200 Kwacha per night (under 10 Euros), but lacked cleanliness and had no running water.
A Frustrating Bus Experience
We booked a 4 A.M. bus to Lusaka with Jkas, supposedly the best company. However, when we arrived at the station at 3:28 A.M., the bus was already gone. The staff had lied, telling us the bus left at 4 A.M. but actually departing at 3 A.M. They then offered an overpriced taxi to chase the bus, which we declined.
 Photo above: between Dodoma and Mbeya.
Photo above: between Dodoma and Mbeya.With no other options left, we searched for an alternative and eventually made our way to the PowerTools bus station — only to find that the bus also had already left.
The next bus? Overnight.
We were stuck.
The Boda Chase
That’s when a Boda driver approached us. He had been waiting at the Powertools station, watching the situation unfold. “I know where your bus is,” he said. “At the checkpoint. I can take you.”
There was no time to think. We climbed on.
The night was pitch black, the streets slick with rain and mud. As soon as he twisted the throttle, the bike lurched forward. The driver wasn’t smooth — he was riding like a madman, shaking left and right as he weaved through the darkness. The wet road made it worse, and the mud felt like a trap waiting to swallow us whole.
 Photo above: between Dodoma and Mbeya.
Photo above: between Dodoma and Mbeya.A gust of wind blew my hat into my face, blinding me for the most time. My gut twisted — I could almost see the crash before it happened. “Slow down!” I shouted. He eased off for a while, but soon enough, he hit the gas again. “I said slow down!” I had to remind him.
It felt like an eternity. The only thought keeping me together was the hope that the checkpoint was close.
Then — buses. Dozens of them.
We told him which one was ours, but in the dim light, they all looked the same. He swerved between them, searching, until finally — Jkas.
 Photo above: the old church in Mbeya.
Photo above: the old church in Mbeya.As we pulled up, the driver suddenly changed his price from 200 to 400 Kwacha. Of course. I handed him 300, not in the mood to argue, and walked straight into the bus, relieved to be off that death ride.
The journey continued, but the morning’s chaos was a reminder that travel in Africa often requires patience and adaptability.
Final Thoughts
The journey from Arusha to Lusaka was long and filled with challenges — delayed buses, unreliable accommodations, and frustrating border experiences. Yet, the beauty of Tanzania and Zambia, the people I met, and the lessons I learned along the way made it all worthwhile. Traveling in Africa requires flexibility, but it rewards you with unforgettable experiences and stories to tell.
 Photo above: in Mbeya.
Photo above: in Mbeya. Photo above: somewhere in Zambia from the Bus.
Photo above: somewhere in Zambia from the Bus. Photo above: in Lusaka.
Photo above: in Lusaka. Photo above: in the East Park Mall in Lusaka.
Photo above: in the East Park Mall in Lusaka. Photo above: in the East Park Mall in Lusaka.
Photo above: in the East Park Mall in Lusaka. Photo above: East Park Mall in Lusaka.
Photo above: East Park Mall in Lusaka. Photo above: in the market in Lusaka.
Photo above: in the market in Lusaka. -
 @ d360efec:14907b5f
2025-02-14 05:35:13
@ d360efec:14907b5f
2025-02-14 05:35:13ภาพรวม LUNCUSDT (OKX):
LUNCUSDT กำลังอยู่ในช่วงที่ผันผวนและมีความไม่แน่นอนสูง หลังจากที่เคยมีสัญญาณบวกของการกลับตัวใน TF Day แต่ตอนนี้ทั้ง 3 Timeframes แสดงให้เห็นถึงแรงขายที่เข้ามา และแนวโน้มเริ่มไม่ชัดเจน
วิเคราะห์ทีละ Timeframe:
(1) TF Day (รายวัน): https://www.tradingview.com/x/ulqLh1c9/
- แนวโน้ม: เริ่มไม่แน่นอน (จากเดิมที่เป็น Early Uptrend) หลังจากที่ราคาไม่สามารถยืนเหนือ EMA 50/200 ได้
- SMC:
- Break of Structure (BOS): มี BOS ทั้งด้านบนและด้านล่าง
- Change of Character (CHoCH): มี CHoCH ด้านบน
- Higher High (HH) & Higher Low (HL): HH ล่าสุดต่ำกว่า High ก่อนหน้า
- EMA:
- EMA 50 และ EMA 200 เคยเป็นแนวรับ แต่ตอนนี้ราคากลับลงมาอยู่ใต้เส้น EMA ทั้งสอง
- Money Flow (LuxAlgo):
- เริ่มมีแท่งสีแดงยาวขึ้น แสดงถึงแรงขายที่เข้ามา
- Volume Profile:
- Volume หนาแน่นบริเวณ 0.00012000 - 0.00014000 (แนวต้าน)
- แท่งเทียน:
- แท่งเทียนล่าสุดเป็นสีแดง แสดงถึงแรงขาย
- แนวรับ: บริเวณ 0.00006000-0.00007000
- แนวต้าน: EMA 50, EMA 200, 0.00014000, 0.00017953
- สรุป: แนวโน้มเริ่มไม่แน่นอน, สัญญาณการกลับตัวเริ่มอ่อนแอ, แรงขายเริ่มเข้ามา
(2) TF4H (4 ชั่วโมง): https://www.tradingview.com/x/SLsNzZi2/
- แนวโน้ม: ขาลง (Downtrend) หลังจากราคาหลุด EMA 50
- SMC:
- Break of Structure (BOS): มี BOS ด้านล่าง
- Change of Character (CHoCH): ไม่ชัดเจน
- Lower Highs (LH) และ Lower Lows (LL)
- EMA:
- EMA 50 และ EMA 200 กลายเป็นแนวต้าน
- Money Flow (LuxAlgo):
- สีแดงเป็นส่วนใหญ่ แสดงถึงแรงขาย
- Volume Profile:
- Volume ค่อนข้างนิ่ง
- แท่งเทียน:
- แท่งเทียนล่าสุดเป็นสีแดง แสดงถึงแรงขาย
- แนวรับ: บริเวณ 0.00006000-0.00007000
- แนวต้าน: EMA 50, EMA 200, บริเวณ High ก่อนหน้า
- สรุป: แนวโน้มขาลง, แรงขายมีอิทธิพล
(3) TF15 (15 นาที): https://www.tradingview.com/x/H8QdIEAL/
- แนวโน้ม: ขาลง (Downtrend)
- SMC:
- Break of Structure (BOS): มี BOS ด้านล่าง
- Change of Character (CHoCH): มีทั้งด้านบนและด้านล่าง
- Lower Highs (LH) และ Lower Lows (LL)
- EMA:
- EMA 50 และ EMA 200 เป็นแนวต้าน
- Money Flow (LuxAlgo):
- สีแดงเป็นส่วนใหญ่ แสดงถึงแรงขาย
- Volume:
- Volume ค่อนข้างเบาบาง
- แนวรับ: บริเวณ Low ล่าสุด
- แนวต้าน: EMA 50, EMA 200, บริเวณ High ก่อนหน้า
- สรุป: แนวโน้มขาลง, แรงขายมีอิทธิพล
สรุปภาพรวมและกลยุทธ์ (LUNCUSDT):
- แนวโน้มหลัก: เริ่มไม่แน่นอน (TF Day), ขาลง (TF4H, TF15)
- Money Flow:
- Day: แรงขายเริ่มเข้ามา
- 4H: แรงขายมีอิทธิพล
- 15m: แรงขายมีอิทธิพล
- กลยุทธ์:
- Wait & See (ดีที่สุด): รอความชัดเจน
- Short (เสี่ยงสูง): ถ้าไม่สามารถ Breakout EMA/แนวต้านได้
- ไม่แนะนำให้ Buy: จนกว่าจะมีสัญญาณกลับตัวที่ชัดเจน
คำแนะนำ:
- LUNC มีความเสี่ยงสูงมาก
- ความขัดแย้งของ Timeframes: Day เริ่มไม่แน่นอน, 4H และ 15m เป็นขาลง
- ถ้าไม่แน่ใจ อย่าเพิ่งเข้าเทรด
Disclaimer:* การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-
 @ d360efec:14907b5f
2025-02-14 05:21:58
@ d360efec:14907b5f
2025-02-14 05:21:58ภาพรวม XRPUSDT (OKX):
XRPUSDT กำลังแสดงสัญญาณที่น่าสนใจและมีความซับซ้อน แนวโน้มใน Timeframe ใหญ่ (Day) เริ่มเป็นขาขึ้น แต่ Timeframe กลาง (4H) เริ่มอ่อนแรง และ Timeframe เล็ก (15m) เป็นขาลง ทำให้เกิดความขัดแย้งที่ต้องระมัดระวัง
วิเคราะห์ทีละ Timeframe:
(1) TF Day (รายวัน): https://www.tradingview.com/x/3EbxjOgV/
- แนวโน้ม: เริ่มเป็นขาขึ้น (Early Uptrend) หลังจากราคา Breakout EMA 50 ขึ้นมาได้
- SMC:
- Break of Structure (BOS): มี BOS ด้านบน (Breakout EMA 50)
- Change of Character (CHoCH): ยังไม่ชัดเจน
- Higher High (HH) & Higher Low (HL): เพิ่งเริ่มก่อตัว (ยังไม่ชัดเจน)
- EMA:
- ราคาอยู่เหนือ EMA 50 (สีเหลือง) และ EMA 200 (สีขาว)
- EMA 50 และ EMA 200 กำลังจะเกิด Golden Cross
- Money Flow (LuxAlgo):
- สีเขียวเป็นส่วนใหญ่ แสดงถึงแรงซื้อที่ยังคงมีอยู่
- มีแท่งสีแดงแทรกบ้าง แสดงถึงการขายทำกำไร
- Volume Profile:
- Volume หนาแน่นบริเวณ EMA 50
- แท่งเทียน:
- แท่งเทียนล่าสุดเป็นสีเขียว แสดงถึงแรงซื้อ
- แนวรับ: EMA 50, EMA 200
- แนวต้าน: 0.6448 (High ก่อนหน้า)
- สรุป: แนวโน้มเริ่มเป็นขาขึ้น แต่ยังอยู่ในช่วงเริ่มต้น
(2) TF4H (4 ชั่วโมง): https://www.tradingview.com/x/nARcdWWp/
- แนวโน้ม: เริ่มไม่แน่นอน (พักตัว, ทดสอบแนวรับ) หลังจากเป็นขาขึ้นระยะสั้น
- SMC:
- Break of Structure (BOS): มี BOS ด้านบน (ก่อนหน้านี้)
- Change of Character (CHoCH): ไม่ชัดเจน
- Higher High (HH) & Higher Low (HL): เริ่มไม่ชัดเจน
- มี Equal Highs (EQH)
- EMA:
- EMA 50 กำลังถูกทดสอบ
- EMA 200 เป็นแนวรับถัดไป
- Money Flow (LuxAlgo):
- เขียวและแดงผสมกัน แสดงถึงความไม่แน่นอน
- แท่งสีแดงเริ่มยาวขึ้น แสดงถึงแรงขายที่เข้ามา
- Volume Profile:
- Volume หนาแน่นบริเวณ EMA 50
- แท่งเทียน:
- แท่งเทียนล่าสุด เป็น Doji
- แนวรับ: EMA 50, EMA 200, บริเวณ 0.50-0.52
- แนวต้าน: บริเวณ High ก่อนหน้า
- สรุป: แนวโน้มเริ่มไม่แน่นอน, มีแรงขายเข้ามา, EMA 50 เป็นจุดสำคัญ
(3) TF15 (15 นาที): https://www.tradingview.com/x/NI2wqamj/
- แนวโน้ม: ขาลง (Downtrend) ระยะสั้น
- SMC:
- Break of Structure (BOS): มี BOS ด้านล่าง
- Change of Character (CHoCH): มีทั้งด้านบนและด้านล่าง
- Lower Highs (LH) และ Lower Lows (LL)
- EMA:
- EMA 50 และ EMA 200 กลายเป็นแนวต้าน
- Money Flow (LuxAlgo):
- สีแดงเป็นส่วนใหญ่ แสดงถึงแรงขาย
- Volume Profile:
- Volume สูง
- แนวรับ: บริเวณ Low ล่าสุด
- แนวต้าน: EMA 50, EMA 200, บริเวณ 0.54
- สรุป: แนวโน้มขาลง, แรงขายมีอิทธิพล
สรุปภาพรวมและกลยุทธ์ (XRPUSDT):
- แนวโน้มหลัก (Day): เริ่มเป็นขาขึ้น
- แนวโน้มรอง (4H): เริ่มไม่แน่นอน, พักตัว
- แนวโน้มระยะสั้น (15m): ขาลง
- Money Flow:
- Day: แรงซื้อยังคงมี
- 4H: แรงซื้อและแรงขายผสมกัน, แรงขายเริ่มเข้ามา
- 15m: แรงขายมีอิทธิพล
- กลยุทธ์:
- Wait & See (ดีที่สุด): รอความชัดเจน
- Buy on Dip (Day, 4H) - เสี่ยงสูงมาก: ต้องรอสัญญาณกลับตัวใน TF15
- Short (15m, เสี่ยงสูง): ถ้าไม่สามารถ Breakout EMA/แนวต้านได้
คำแนะนำ:
- ความขัดแย้งของ Timeframes: ยังคงมีอยู่
- Money Flow: Day เป็นบวก, 4H เริ่มไม่แน่นอน, 15m เป็นลบ
- EMA 50 (TF4H): จุดสำคัญ
- ถ้าไม่แน่ใจ อย่าเพิ่งเข้าเทรด
Disclaimer:* การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-
 @ 9e69e420:d12360c2
2025-02-13 23:01:36
@ 9e69e420:d12360c2
2025-02-13 23:01:36Robert F. Kennedy Jr. has been confirmed as the next Secretary of Health and Human Services with a Senate vote of 52-48. Senator Mitch McConnell opposed the confirmation. Kennedy's nomination faced hurdles but gained support from the Senate Finance Committee.
During the confirmation hearing, Senator Rand Paul criticized the oversimplification of vaccine discussions. He stated, "Discussion over vaccines is so oversimplified and dumbed down." Kennedy asserted his support for vaccines like measles and polio, promising not to discourage vaccinations as HHS Secretary. Previously, he switched from the Democratic Party to run as an independent and endorsed Trump
-
 @ d360efec:14907b5f
2025-02-13 11:15:12
@ d360efec:14907b5f
2025-02-13 11:15:12Top-Down Analysis: กลยุทธ์การเทรดเพื่อมองภาพรวมและจับจังหวะทำกำไร
ในโลกของการเทรดที่เต็มไปด้วยความผันผวน การมีเครื่องมือวิเคราะห์ที่แข็งแกร่งเป็นสิ่งสำคัญอย่างยิ่งที่จะช่วยนำทางให้เทรดเดอร์สามารถตัดสินใจได้อย่างมีหลักการและเพิ่มโอกาสในการทำกำไร หนึ่งในเครื่องมือที่ได้รับความนิยมและมีประสิทธิภาพคือ "Top-Down Analysis" หรือการวิเคราะห์จากบนลงล่าง ซึ่งเป็นวิธีการมองภาพรวมของตลาดก่อนที่จะเจาะจงไปที่สินทรัพย์ที่เราสนใจ บทความนี้จะพาคุณไปทำความเข้าใจกับ Top-Down Analysis อย่างละเอียด พร้อมทั้งแนะนำกลยุทธ์การเทรดที่สามารถนำไปปรับใช้ได้จริง
Top-Down Analysis คืออะไร?
Top-Down Analysis เป็นกระบวนการวิเคราะห์ตลาดที่เริ่มต้นจากการพิจารณาภาพรวมในกรอบเวลาที่ใหญ่ขึ้น ก่อนที่จะค่อยๆ ย่อยลงไปในกรอบเวลาที่เล็กลง เพื่อทำความเข้าใจบริบทของตลาดและหาจังหวะการเทรดที่เหมาะสม วิธีการนี้ช่วยให้เทรดเดอร์สามารถมองเห็นทิศทางหลักของตลาด, แนวโน้มที่กำลังเกิดขึ้น, ระดับราคาสำคัญ, และความสมดุลระหว่างอุปสงค์และอุปทาน ก่อนที่จะตัดสินใจเข้าเทรดในกรอบเวลาที่เล็กลง
องค์ประกอบสำคัญของ Top-Down Analysis (อ้างอิงจากภาพ)
ภาพ "Top-Down Analysis" ได้สรุปองค์ประกอบสำคัญของการวิเคราะห์นี้ไว้อย่างชัดเจน โดยแบ่งการวิเคราะห์ออกเป็น 3 กรอบเวลาหลัก: 4 ชั่วโมง (4H), 1 ชั่วโมง (1H), และ 15 นาที (15min) แต่ละกรอบเวลามีองค์ประกอบที่ต้องพิจารณาดังนี้:
-
กรอบเวลา 4 ชั่วโมง (4H): ภาพรวมตลาดและทิศทางหลัก ในกรอบเวลา 4 ชั่วโมง เราจะเน้นการวิเคราะห์ภาพรวมของตลาด เพื่อกำหนดทิศทางหลักและแนวโน้มในระยะกลาง องค์ประกอบสำคัญในกรอบเวลานี้คือ:
- Direction (ทิศทาง): ประเมินทิศทางที่ตลาดกำลังเคลื่อนที่ไป โดยพิจารณาจากแนวโน้มและโครงสร้างราคาในภาพรวม ตลาดกำลังเป็นขาขึ้น, ขาลง หรืออยู่ในช่วง Sideways?
- Trend (แนวโน้ม): ระบุแนวโน้มหลักของตลาด ไม่ว่าจะเป็นแนวโน้มขาขึ้น (Uptrend), แนวโน้มขาลง (Downtrend) หรือ Sideways การเข้าใจแนวโน้มช่วยในการกำหนดกลยุทธ์การเทรดที่เหมาะสม
- Key levels (ระดับราคาสำคัญ): หาระดับราคาแนวรับและแนวต้านที่สำคัญในกรอบเวลา 4 ชั่วโมง ระดับเหล่านี้มักเป็นจุดที่ราคาเคยมีการกลับตัวหรือพักตัวในอดีต และอาจเป็นบริเวณที่ราคาจะตอบสนองอีกครั้งในอนาคต
- Supply & Demand (อุปทานและอุปสงค์): วิเคราะห์ความสมดุลระหว่างแรงซื้อ (Demand) และแรงขาย (Supply) ในตลาด โดยพิจารณาจากพฤติกรรมราคาบริเวณแนวรับแนวต้าน และสัญญาณจากเครื่องมือวิเคราะห์อื่นๆ (ถ้าใช้)
-
กรอบเวลา 1 ชั่วโมง (1H): หาจังหวะและบริเวณที่น่าสนใจ เมื่อได้ภาพรวมและทิศทางหลักจากกรอบ 4H แล้ว เราจะย่อยลงมาในกรอบ 1 ชั่วโมง เพื่อหาจังหวะการเทรดที่สอดคล้องกับทิศทางหลัก และมองหารูปแบบราคาที่น่าสนใจ องค์ประกอบสำคัญในกรอบเวลานี้คือ:
- Breaks (การทะลุ): สังเกตการทะลุแนวรับแนวต้าน หรือระดับราคาสำคัญในกรอบ 1H ที่สอดคล้องกับทิศทางหลักใน 4H การทะลุเหล่านี้อาจเป็นสัญญาณของการเคลื่อนไหวครั้งใหญ่ของราคา
- Reversals (การกลับตัว): มองหารูปแบบการกลับตัวของราคาที่อาจเกิดขึ้นบริเวณระดับราคาสำคัญในกรอบ 1H ซึ่งบ่งบอกถึงจุดสิ้นสุดของแนวโน้มปัจจุบันและเริ่มต้นแนวโน้มใหม่
- OB (Order Blocks): ระบุบริเวณ Order Blocks ในกรอบ 1H ซึ่งเป็นพื้นที่ที่มีการสั่งซื้อขายจำนวนมากในอดีต Order Blocks เหล่านี้มักจะทำหน้าที่เป็นแนวรับแนวต้านในอนาคต
- FVG (Fair Value Gaps): มองหา Fair Value Gaps ในกรอบ 1H ซึ่งเป็นช่องว่างของราคาที่เกิดจากการเคลื่อนไหวอย่างรวดเร็ว FVG มักจะเป็นเป้าหมายของราคาในอนาคต เนื่องจากราคาอาจจะกลับมาปิดช่องว่างเหล่านี้
- Liquidity (สภาพคล่อง): ประเมินสภาพคล่องบริเวณระดับราคาที่เราสนใจในกรอบ 1H บริเวณที่มีสภาพคล่องสูงมักจะดึงดูดนักลงทุนรายใหญ่ และอาจทำให้เกิดการเคลื่อนไหวของราคาที่รุนแรง
-
กรอบเวลา 15 นาที (15min): ยืนยันสัญญาณและหาจุดเข้าเทรด ในกรอบเวลา 15 นาที เราจะเน้นการยืนยันสัญญาณการเทรด และหาจุดเข้าเทรดที่แม่นยำ เพื่อลดความเสี่ยงในการเข้าเทรดเร็วเกินไป องค์ประกอบสำคัญในกรอบเวลานี้คือ:
-
Confirmation (การยืนยัน): รอสัญญาณยืนยันการเคลื่อนไหวของราคาในกรอบ 15 นาที ที่สอดคล้องกับการวิเคราะห์ในกรอบ 1H และ 4H สัญญาณยืนยันอาจมาในรูปแบบของแท่งเทียนกลับตัว, รูปแบบ Chart Patterns, หรือสัญญาณจาก Indicators
- จุดเข้าเทรด: เมื่อมีสัญญาณยืนยันที่ชัดเจนในกรอบ 15 นาที และสอดคล้องกับการวิเคราะห์ในกรอบเวลาที่ใหญ่ขึ้น จึงตัดสินใจเข้าเทรด โดยกำหนด Stop Loss เพื่อจำกัดความเสี่ยง และ Take Profit เพื่อตั้งเป้าหมายในการทำกำไร
กลยุทธ์การเทรด Top-Down Analysis: ขั้นตอนสู่ความสำเร็จ
เพื่อนำ Top-Down Analysis ไปใช้ในการเทรดอย่างมีประสิทธิภาพ เราสามารถทำตามขั้นตอนต่อไปนี้:
-
เริ่มต้นที่ 4H: กำหนดทิศทางและแนวโน้มหลัก วิเคราะห์กราฟ 4H เพื่อระบุทิศทางหลักของตลาด แนวโน้ม และระดับราคาสำคัญ ประเมินความสมดุลของ Supply & Demand เพื่อกำหนด Bias การเทรด (เน้นซื้อหรือขาย)
-
เจาะลึก 1H: หาจังหวะและบริเวณที่น่าสนใจ เมื่อได้ทิศทางหลักจาก 4H แล้ว ให้ย่อยลงมาดูกราฟ 1H เพื่อหารูปแบบราคาที่น่าสนใจ เช่น การทะลุแนวรับแนวต้าน, รูปแบบการกลับตัว, Order Blocks, Fair Value Gaps และบริเวณที่มีสภาพคล่องสูง
-
ยืนยันใน 15min: หาจุดเข้าเทรดที่แม่นยำ รอสัญญาณยืนยันในกรอบ 15 นาที ที่สอดคล้องกับการวิเคราะห์ในกรอบเวลาที่ใหญ่ขึ้น ใช้ Price Action, แท่งเทียน, หรือ Indicators เพื่อยืนยันสัญญาณ และหาจุดเข้าเทรดที่แม่นยำ พร้อมกำหนด Stop Loss และ Take Profit ที่เหมาะสม
ประโยชน์ของการใช้ Top-Down Analysis * มองเห็นภาพรวมตลาด: ช่วยให้เทรดเดอร์เข้าใจบริบทของตลาดในภาพรวม ไม่หลงทางในรายละเอียดเล็กๆ น้อยๆ * ตัดสินใจเทรดอย่างมีหลักการ: ทำให้การตัดสินใจเทรดมีเหตุผลและมีข้อมูลสนับสนุนมากขึ้น ไม่ใช่แค่การคาดเดา * เพิ่มความแม่นยำในการเทรด: การวิเคราะห์หลายกรอบเวลาช่วยกรองสัญญาณรบกวน และเพิ่มโอกาสในการเข้าเทรดในทิศทางที่ถูกต้อง * ลดความเสี่ยง: ช่วยลดโอกาสในการเทรดสวนทางแนวโน้มหลักของตลาด และช่วยในการกำหนด Stop Loss ที่เหมาะสม
ข้อควรจำและข้อควรระวัง * ฝึกฝนและสังเกต: Top-Down Analysis ต้องอาศัยการฝึกฝนและการสังเกตกราฟราคาอย่างสม่ำเสมอ เพื่อพัฒนาความเข้าใจและทักษะในการวิเคราะห์ * ปรับใช้ให้เข้ากับสไตล์: ปรับกลยุทธ์ให้เข้ากับสไตล์การเทรดของคุณ และสินทรัพย์ที่คุณเทรด * บริหารความเสี่ยง: ให้ความสำคัญกับการบริหารความเสี่ยงเสมอ กำหนดขนาด Position ที่เหมาะสม และใช้ Stop Loss ทุกครั้ง * ไม่มีกลยุทธ์ใดสมบูรณ์แบบ: Top-Down Analysis เป็นเครื่องมือที่มีประสิทธิภาพ แต่ไม่มีกลยุทธ์ใดที่รับประกันผลกำไร 100% การเทรดมีความเสี่ยง โปรดศึกษาและทำความเข้าใจความเสี่ยงก่อนตัดสินใจลงทุน
สรุป Top-Down Analysis เป็นกลยุทธ์การเทรดที่ทรงพลัง ซึ่งช่วยให้เทรดเดอร์สามารถวิเคราะห์ตลาดอย่างเป็นระบบ มองภาพรวม และจับจังหวะการเทรดได้อย่างแม่นยำ การนำหลักการของ Top-Down Analysis ไปปรับใช้ในการเทรด จะช่วยเพิ่มประสิทธิภาพในการตัดสินใจ และเพิ่มโอกาสในการประสบความสำเร็จในตลาดการเงินได้อย่างยั่งยืน
-
-
 @ e3ba5e1a:5e433365
2025-02-13 06:16:49
@ e3ba5e1a:5e433365
2025-02-13 06:16:49My favorite line in any Marvel movie ever is in “Captain America.” After Captain America launches seemingly a hopeless assault on Red Skull’s base and is captured, we get this line:
“Arrogance may not be a uniquely American trait, but I must say, you do it better than anyone.”
Yesterday, I came across a comment on the song Devil Went Down to Georgia that had a very similar feel to it:

America has seemingly always been arrogant, in a uniquely American way. Manifest Destiny, for instance. The rest of the world is aware of this arrogance, and mocks Americans for it. A central point in modern US politics is the deriding of racist, nationalist, supremacist Americans.
That’s not what I see. I see American Arrogance as not only a beautiful statement about what it means to be American. I see it as an ode to the greatness of humanity in its purest form.
For most countries, saying “our nation is the greatest” is, in fact, twinged with some level of racism. I still don’t have a problem with it. Every group of people should be allowed to feel pride in their accomplishments. The destruction of the human spirit since the end of World War 2, where greatness has become a sin and weakness a virtue, has crushed the ability of people worldwide to strive for excellence.
But I digress. The fears of racism and nationalism at least have a grain of truth when applied to other nations on the planet. But not to America.
That’s because the definition of America, and the prototype of an American, has nothing to do with race. The definition of Americanism is freedom. The founding of America is based purely on liberty. On the God-given rights of every person to live life the way they see fit.
American Arrogance is not a statement of racial superiority. It’s barely a statement of national superiority (though it absolutely is). To me, when an American comments on the greatness of America, it’s a statement about freedom. Freedom will always unlock the greatness inherent in any group of people. Americans are definitionally better than everyone else, because Americans are freer than everyone else. (Or, at least, that’s how it should be.)
In Devil Went Down to Georgia, Johnny is approached by the devil himself. He is challenged to a ridiculously lopsided bet: a golden fiddle versus his immortal soul. He acknowledges the sin in accepting such a proposal. And yet he says, “God, I know you told me not to do this. But I can’t stand the affront to my honor. I am the greatest. The devil has nothing on me. So God, I’m gonna sin, but I’m also gonna win.”
Libertas magnitudo est
-
 @ d360efec:14907b5f
2025-02-13 05:54:17
@ d360efec:14907b5f
2025-02-13 05:54:17
ภาพรวม LUNCUSDT (OKX):
LUNCUSDT กำลังอยู่ในช่วงที่ มีความผันผวนสูงและมีความไม่แน่นอนมาก แม้ว่าในอดีต (TF Day) จะเคยมีสัญญาณของการพยายามกลับตัวเป็นขาขึ้น (Breakout EMA 50 และเกิด Golden Cross) แต่ปัจจุบันแรงซื้อเหล่านั้นเริ่มอ่อนแรงลง และมีแรงขายเข้ามาในตลาดมากขึ้น ทำให้เกิดความขัดแย้งระหว่าง Timeframes ต่างๆ

สถานะปัจจุบัน:
- แนวโน้ม:
- TF Day: เริ่มไม่แน่นอน (จากเดิมที่เป็น Early Uptrend) - แม้ว่าราคาจะยังอยู่เหนือ EMA 50/200 แต่ Money Flow เริ่มแสดงสัญญาณเตือน
- TF4H: เริ่มไม่แน่นอน (พักตัว, ทดสอบแนวรับ EMA 50) - Money Flow บ่งบอกถึงแรงขายที่เข้ามา
- TF15: ผันผวนสูง, ไม่มีทิศทางชัดเจน (Sideways) - Money Flow แสดงถึงแรงขาย แต่ก็มีแรงซื้อกลับเข้ามาบ้าง
- Money Flow (LuxAlgo):
- TF Day: แรงซื้อเริ่มอ่อนแรงลงอย่างมีนัยสำคัญ, มีแรงขายเข้ามา
- TF4H: แรงขายมีมากกว่าแรงซื้อ
- TF15: แรงขายและแรงซื้อผสมกัน, โดยรวมแรงขายยังมากกว่า
- EMA:
- TF Day: EMA 50/200 เป็นแนวรับ/แนวต้าน
- TF4H: EMA 50 กำลังถูกทดสอบ, EMA 200 เป็นแนวต้าน
- TF15: EMA 50/200 เป็นแนวต้าน
โครงสร้างราคา (SMC):
| Timeframe | Break of Structure (BOS) | Change of Character (CHoCH) | Higher High (HH) & Higher Low (HL) | Equal Highs (EQH) / Equal Lows (EQL) | | :-------- | :----------------------- | :--------------------------- | :----------------------------------- | :------------------------------------- | | Day | ด้านบนและล่าง | ด้านบน | เริ่มก่อตัว (แต่ไม่แข็งแกร่ง) | - | | 4H | ด้านบน | ด้านบน | เริ่มก่อตัว (แต่ไม่ชัดเจน) | มี EQH หลายจุด | | 15m | ด้านบนและล่าง | มีทั้งบนและล่าง | Lower Highs (LH) & Lower Lows (LL) | มี EQH และ EQL หลายจุด |
แนวรับ-แนวต้านสำคัญ:
| Timeframe | แนวรับ | แนวต้าน | | :-------- | :----------------------------------------------------------- | :--------------------------------------------------------------------- | | Day | EMA 50 (≈0.00010000), EMA 200 (≈0.00008000), 0.00006000-0.00007000 | 0.00017953 (High ล่าสุด), 0.00014000 (Volume Profile) | | 4H | EMA 50 (≈0.00007000), 0.00006000-0.00007000 | EMA 200 (≈0.00008000), 0.00008132, บริเวณ 0.00010000-0.00012000 (EQH) | | 15m | บริเวณ Low ล่าสุด | EMA 50, EMA 200, บริเวณ 0.000075-0.000076 (EQH) |
กลยุทธ์ (LUNCUSDT):
- Wait & See (ทางเลือกที่ดีที่สุด):
- เหตุผล: ความขัดแย้งระหว่าง Timeframes สูงมาก, แนวโน้มไม่ชัดเจน, Money Flow ใน TF4H และ TF15 เป็นลบ
- รอให้ราคาแสดงทิศทางที่ชัดเจนกว่านี้ (ยืนเหนือ EMA 50 ใน TF4H ได้, Breakout แนวต้านใน TF15)
- Buy on Dip (Day, 4H) - ความเสี่ยงสูงมาก ไม่แนะนำ:
- เหตุผล: แนวโน้มระยะยาวอาจจะยังเป็นขาขึ้นได้ (ถ้าไม่หลุดแนวรับสำคัญ)
- เงื่อนไข: ต้อง รอสัญญาณการกลับตัวใน TF15 ก่อน
- จุดเข้า: พิจารณาเฉพาะบริเวณแนวรับที่แข็งแกร่งมากๆ (EMA ของ Day/4H) และต้องดู TF15 ประกอบ
- Stop Loss: ต่ำกว่า Low ล่าสุดของ TF15
- Short (15, ความเสี่ยงสูงมาก):
- เหตุผล: แนวโน้ม TF15 เป็นขาลง, Money Flow เป็นลบ
- เงื่อนไข: ราคาไม่สามารถ Breakout EMA หรือแนวต้านอื่นๆ ใน TF15 ได้
- จุดเข้า: บริเวณ EMA หรือแนวต้านของ TF15
- Stop Loss: เหนือ High ล่าสุดของ TF15
คำแนะนำ (เน้นย้ำ):
- LUNC เป็นเหรียญที่มีความเสี่ยงสูงมาก (High Risk): มีความผันผวนสูง และอาจมีการเปลี่ยนแปลงอย่างรวดเร็ว
- ความขัดแย้งของ Timeframes: สถานการณ์ของ LUNCUSDT มีความขัดแย้งสูงมาก และมีความเสี่ยงสูง
- Money Flow: บ่งบอกถึงแรงขายที่เริ่มเข้ามา และแนวโน้มขาขึ้น (ระยะกลาง-ยาว) ที่อ่อนแอลง
- ถ้าไม่แน่ใจ อย่าเพิ่งเข้าเทรด: "รอ" เป็นกลยุทธ์ที่ดีที่สุด
- Risk Management: สำคัญที่สุด ไม่ว่าจะเลือกกลยุทธ์ใด ต้องมีการบริหารความเสี่ยงที่ดี
สรุป: LUNCUSDT กำลังอยู่ในช่วงเวลาที่ยากลำบากและมีความเสี่ยงสูงมากที่สุดในบรรดา 3 เหรียญที่เราวิเคราะห์กันมา การตัดสินใจที่ผิดพลาดอาจนำไปสู่การขาดทุนได้ ควรพิจารณาอย่างรอบคอบก่อนเข้าเทรดทุกครั้ง และ "รอ" จนกว่าจะมีสัญญาณที่ชัดเจนกว่านี้ เป็นทางเลือกที่ปลอดภัยที่สุดสำหรับนักลงทุนส่วนใหญ่ค่ะ
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
- แนวโน้ม:
-
 @ d360efec:14907b5f
2025-02-13 05:27:39
@ d360efec:14907b5f
2025-02-13 05:27:39
ภาพรวม XRPUSDT (OKX):
XRPUSDT กำลังอยู่ในช่วงสำคัญ แนวโน้มระยะยาว (TF Day) เริ่มมีสัญญาณบวกของการเป็นขาขึ้น (Early Uptrend) หลังราคา Breakout EMA 50 และ Money Flow สนับสนุน อย่างไรก็ตาม แนวโน้มระยะกลาง (TF4H) เริ่มแสดงความอ่อนแอลง โดยราคาพักตัวลงมาทดสอบแนวรับสำคัญ และ Money Flow บ่งชี้ถึงแรงซื้อที่ลดลงและแรงขายที่เพิ่มขึ้น ส่วนแนวโน้มระยะสั้นมาก (TF15) เป็นขาลงชัดเจน

แนวโน้ม:
- TF Day: เริ่มเป็นขาขึ้น (Early Uptrend) - Breakout EMA 50, Money Flow เป็นบวก
- TF4H: เริ่มไม่แน่นอน (พักตัว, ทดสอบแนวรับ EMA 50 และ EQL) - Money Flow เริ่มเป็นลบ
- TF15: ขาลง (Downtrend) ระยะสั้นมาก - ราคาหลุด EMA, โครงสร้างราคาเป็น Lower Highs/Lows, Money Flow เป็นลบ
โครงสร้างราคา (SMC):
| Timeframe | Break of Structure (BOS) | Change of Character (CHoCH) | Higher High (HH) & Higher Low (HL) | Equal Highs (EQH) / Equal Lows (EQL) | | :-------- | :----------------------- | :--------------------------- | :----------------------------------- | :------------------------------------- | | Day | ด้านบน (Breakout EMA 50) | ไม่ชัดเจน | เริ่มก่อตัว (แต่ยังไม่ชัดเจน) | - | | 4H | ด้านบน | ไม่ชัดเจน | เริ่มก่อตัว (แต่ไม่ชัดเจน) | EQH: 3.00-3.20, EQL: 2.2667 | | 15m | ด้านล่าง | มีทั้งบนและล่าง | Lower Highs (LH) & Lower Lows (LL) | EQH: 2.48-2.50, EQL: 2.38 |

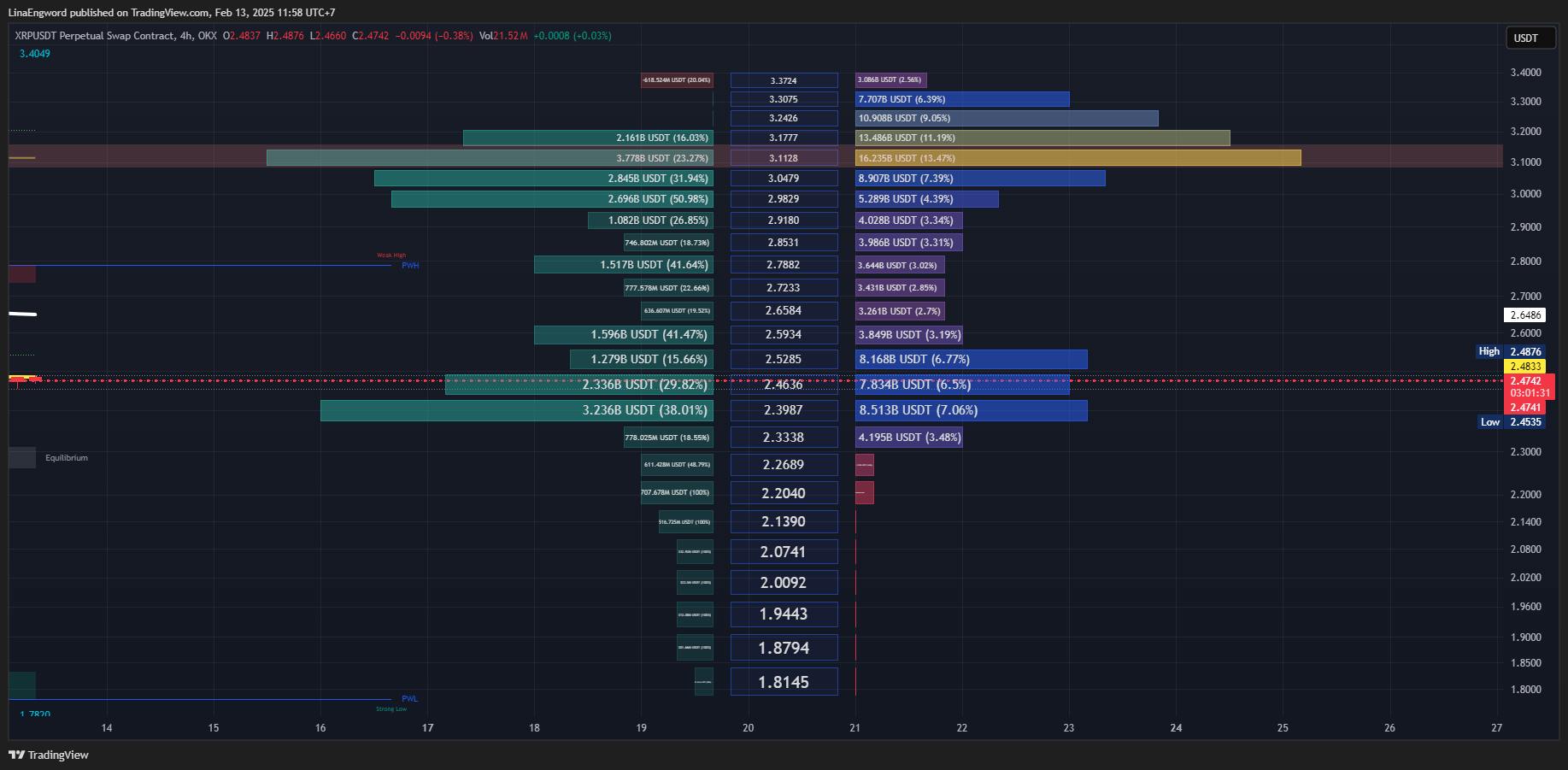
Money Flow (LuxAlgo):
- TF Day: แรงซื้อแข็งแกร่ง
- TF4H: แรงซื้อเริ่มอ่อนแรงลง, แรงขายเริ่มเข้ามา
- TF15: แรงขายมีอิทธิพลเหนือกว่า
EMA (Exponential Moving Average):
- TF Day: EMA 50 & 200 เป็นแนวรับ
- TF4H: EMA 50 กำลังถูกทดสอบ, EMA 200 เป็นแนวรับถัดไป
- TF15: EMA 50 & 200 เป็นแนวต้าน
แนวรับ-แนวต้านสำคัญ:
| Timeframe | แนวรับ | แนวต้าน | | :-------- | :----------------------------------------------------- | :----------------------------------------------------------------------- | | Day | EMA 50 (≈1.56), EMA 200 (≈1.08) | 3.4049 (High), 3.00-3.20 (EQH) | | 4H | EMA 50 (≈2.20), 2.2667 (EQL), EMA 200, 1.7820 | 3.4049, 2.3987 (Volume Profile), 3.00-3.20 (EQH) | | 15m | 2.38 (EQL, Volume Profile), 2.3274 | EMA 50, EMA 200, 2.4196, Equilibrium (≈2.44), 2.48-2.50 (EQH) |
กลยุทธ์ (XRPUSDT):
- Wait & See (ทางเลือกที่ดีที่สุด):
- เหตุผล: ความขัดแย้งระหว่าง Timeframes สูง, TF4H กำลังทดสอบแนวรับสำคัญ, Money Flow ใน TF4H และ TF15 เป็นลบ
- รอให้ราคาแสดงทิศทางที่ชัดเจน (ยืนเหนือ EMA 50 ใน TF4H ได้ หรือ Breakout แนวต้านใน TF15)
- Buy on Dip (Day, 4H) - ความเสี่ยงสูงมาก:
- เหตุผล: แนวโน้มระยะยาวยังมีโอกาสเป็นขาขึ้น, Money Flow ใน TF Day เป็นบวก
- เงื่อนไข (สำคัญมาก): ต้อง รอสัญญาณการกลับตัวใน TF15 ก่อน เช่น:
- Breakout แนวต้านย่อยๆ พร้อม Volume
- Money Flow (TF15) เปลี่ยนเป็นสีเขียว
- Bullish Candlestick Patterns
- จุดเข้า (Day): EMA 50, EMA 200 (ดู TF15 ประกอบ)
- จุดเข้า (4H): EMA 50, 2.2667 (EQL) (ดู TF15 ประกอบ)
- Stop Loss: ต่ำกว่า Low ล่าสุดของ TF15 หรือต่ำกว่าแนวรับที่เข้าซื้อ
- Short (15, ความเสี่ยงสูงมาก):
- เหตุผล: แนวโน้ม TF15 เป็นขาลง, Money Flow เป็นลบ
- เงื่อนไข: ราคาไม่สามารถกลับขึ้นไปยืนเหนือ EMA ของ TF15 ได้
- จุดเข้า: บริเวณ EMA ของ TF15 หรือแนวต้านอื่นๆ
- Stop Loss: เหนือ High ล่าสุดของ TF15
คำแนะนำ:
- ความขัดแย้งของ Timeframes: XRPUSDT มีความขัดแย้งสูงมาก และมีความเสี่ยงสูง
- Money Flow: Day เป็นบวก, 4H เริ่มเป็นลบ, 15m เป็นลบ
- EMA 50 (TF4H) & EQL 2.2667: จุดชี้ชะตา
- ถ้าไม่แน่ใจ อย่าเพิ่งเข้าเทรด: "รอ" ดีที่สุด
- Risk Management: สำคัญที่สุด
สรุป: สถานการณ์ของ XRPUSDT ตอนนี้มีความเสี่ยงสูงมาก และไม่เหมาะกับนักลงทุนที่รับความเสี่ยงได้ต่ำ การ "รอ" จนกว่าจะมีสัญญาณที่ชัดเจนกว่านี้ เป็นทางเลือกที่ปลอดภัยที่สุดค่ะ
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-
 @ d360efec:14907b5f
2025-02-13 04:47:20
@ d360efec:14907b5f
2025-02-13 04:47:20 ภาพรวม BTCUSDT :
ภาพรวม BTCUSDT :Bitcoin (BTCUSDT) กำลังอยู่ในช่วงสำคัญ แม้ว่าแนวโน้มหลักในระยะกลางถึงยาว (TF Day & 4H) จะยังคงเป็นขาขึ้นที่แข็งแกร่ง แต่ในระยะสั้นมาก (TF15) กลับแสดงสัญญาณของความอ่อนแอและการปรับฐานลงมา ทำให้เกิดความไม่แน่นอนในทิศทางของราคา อย่างไรก็ตาม Money Flow ใน TF Day บ่งชี้ว่าแรงซื้อโดยรวมยังคงแข็งแกร่ง

แนวโน้ม:
- TF Day: ขาขึ้น (Uptrend) แข็งแกร่ง – ราคาอยู่เหนือ EMA 50 และ EMA 200, โครงสร้างราคาเป็น Higher Highs (HH) และ Higher Lows (HL), Money Flow เป็นบวก (แรงซื้อ)
- TF4H: ขาขึ้น (Uptrend) – ราคาอยู่เหนือ EMA, มีการพักตัวลงมา (Pullback) แต่ยังไม่เสียโครงสร้างขาขึ้น, Money Flow เริ่มอ่อนแรง (แรงซื้อลดลง, แรงขายเพิ่มขึ้น)
- TF15: ขาลง (Downtrend) ระยะสั้นมาก – ราคาหลุด EMA และแนวรับย่อย, โครงสร้างราคาเป็น Lower Highs (LH) และ Lower Lows (LL), Money Flow เป็นลบ (แรงขาย)
โครงสร้างราคา (SMC):
- TF Day: ยืนยันแนวโน้มขาขึ้น (HH, HL, BOS)
- TF4H: ยืนยันแนวโน้มขาขึ้น (HH, HL, BOS), มี Equal Highs (EQH) ที่เป็นแนวต้าน
- TF15: บ่งบอกถึงแนวโน้มขาลงระยะสั้น (BOS ด้านล่าง, LH, LL), มี EQH เป็นแนวต้าน
Money Flow (LuxAlgo) - สรุป:
- TF Day: แรงซื้อยังคงแข็งแกร่งอย่างชัดเจน
- TF4H: แรงซื้อเริ่มอ่อนแรงลง, มีแรงขายเข้ามา
- TF15: แรงขายมีอิทธิพลเหนือกว่า

EMA (Exponential Moving Average):
- TF Day & 4H: EMA 50 & 200 เป็นแนวรับสำคัญ
- TF15: EMA 50 & 200 กลายเป็นแนวต้าน
แนวรับ-แนวต้านสำคัญ:
| Timeframe | แนวรับ | แนวต้าน | | :-------- | :------------------------------------------------------------------------- | :-------------------------------------------------------------- | | Day | EMA 50, EMA 200, 96,000-98,000, 85,724.7 | 109,998.9 (High เดิม) | | 4H | EMA 50, EMA 200, 96,000-98,000, 89,037.0 | 109,998.9 (EQH, High เดิม) | | 15m | 95,200 (Low ล่าสุด), 94,707.4 (Low ก่อนหน้า) | EMA 50, EMA 200, บริเวณ 96,000, 96,807.8, 97,000-97,200 |
กลยุทธ์ (BTCUSDT):
- Buy on Dip (Day, 4H) - มีความน่าเชื่อถือมากขึ้น แต่ยังคงต้องระมัดระวัง:
- เหตุผล: แนวโน้มหลักยังเป็นขาขึ้น, Money Flow ใน TF Day แข็งแกร่ง
- เงื่อนไข: ยังคงต้องรอสัญญาณการกลับตัวของราคาใน TF15 ก่อน (Breakout แนวต้านย่อย, Money Flow TF15 เป็นบวก, Bullish Candlestick Patterns)
- จุดเข้า (Day): EMA 50, EMA 200, บริเวณ 96,000-98,000
- จุดเข้า (4H): EMA 50
- Stop Loss: ต่ำกว่า Low ล่าสุดของ TF15 หรือต่ำกว่าแนวรับที่เข้าซื้อ
- Short (15, ความเสี่ยงสูงมาก):
- เหตุผล: แนวโน้ม TF15 เป็นขาลง, Money Flow TF15 เป็นลบ
- เงื่อนไข: ราคาไม่สามารถกลับขึ้นไปยืนเหนือ EMA ของ TF15 ได้
- จุดเข้า: บริเวณ EMA ของ TF15 หรือแนวต้านอื่นๆ
- Stop Loss: เหนือ High ล่าสุดของ TF15
- Wait & See (ทางเลือกที่ปลอดภัย):
- เหตุผล: ความขัดแย้งระหว่าง Timeframes ยังคงมีอยู่
- รอให้ตลาดเฉลยทิศทางที่ชัดเจนกว่านี้
คำแนะนำ (เน้นย้ำ):
- Money Flow ใน TF Day: เป็นปัจจัยบวกที่สำคัญ ทำให้กลยุทธ์ Buy on Dip มีน้ำหนักมากขึ้น
- ความขัดแย้งของ Timeframes: ยังคงต้องระวัง TF15 ที่เป็นขาลง
- Volume: การ Breakout/Breakdown ใดๆ ควรมี Volume สนับสนุน
- Risk Management: สำคัญที่สุด
สรุป:
สถานการณ์ของ BTCUSDT โดยรวมยังคงเป็นบวก (ขาขึ้น) แต่มีความเสี่ยงในระยะสั้นจาก TF15 การตัดสินใจลงทุนควรพิจารณาจาก Timeframe ที่เหมาะสมกับสไตล์การเทรดของคุณ และอย่าลืมบริหารความเสี่ยงเสมอค่ะ
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-
 @ d360efec:14907b5f
2025-02-12 07:37:43
@ d360efec:14907b5f
2025-02-12 07:37:43

Bitcoin (BTCUSDT) กำลังอยู่ในช่วงหัวเลี้ยวหัวต่อ แม้ว่าแนวโน้มหลักในระยะกลางถึงยาว (TF Day & 4H) จะยังคงเป็นขาขึ้นที่แข็งแกร่ง แต่ในระยะสั้นมาก (TF15) กลับแสดงสัญญาณของความอ่อนแอและการปรับฐานลงมาอย่างรวดเร็ว
แนวโน้ม: * TF Day: ขาขึ้น (Uptrend) แข็งแกร่ง – ราคาอยู่เหนือ EMA 50 และ EMA 200, โครงสร้างราคาเป็น Higher Highs (HH) และ Higher Lows (HL) อย่างต่อเนื่อง * TF4H: ขาขึ้น (Uptrend) ชัดเจน – ราคาอยู่เหนือ EMA, มีการพักตัวลงมา (Pullback) แต่ยังไม่เสียโครงสร้างขาขึ้น * TF15: ขาลง (Downtrend) ระยะสั้นมาก – ราคาหลุด EMA และแนวรับย่อย, โครงสร้างราคาเริ่มเป็น Lower Highs (LH) และ Lower Lows (LL)
โครงสร้างราคา (SMC): * TF Day: ยืนยันแนวโน้มขาขึ้น (HH, HL, BOS) * TF4H: ยืนยันแนวโน้มขาขึ้น (HH, HL, BOS), มี Equal Highs (EQH) ที่เป็นแนวต้าน * TF15: บ่งบอกถึงแนวโน้มขาลงระยะสั้น (BOS ด้านล่าง, LH, LL), มี EQH เป็นแนวต้าน
Money Flow (LuxAlgo): * TF Day: Money Flow: โดยรวมเป็นสีเขียว แสดงถึงแรงซื้อที่ยังคงมีอิทธิพลเหนือกว่า แต่ก็มีแท่งสีแดงแทรกบ้าง บ่งบอกถึงการขายทำกำไรในบางช่วง * TF4H: Money Flow: โดยรวมเป็นสีเขียว แต่เริ่มมีแท่งสีเขียวสั้นลง และมีแท่งสีแดงยาวขึ้น แสดงว่าแรงซื้อเริ่มอ่อนแรงลง และมีแรงขายเข้ามา * TF15: Money Flow: สีแดงมีอิทธิพลเหนือกว่าสีเขียวอย่างชัดเจน และแท่งสีแดงค่อนข้างยาว แสดงถึงแรงขายที่แข็งแกร่ง
EMA (Exponential Moving Average): * TF Day & 4H: EMA 50 & 200 เป็นแนวรับสำคัญ * TF15: EMA 50 & 200 กลายเป็นแนวต้าน หลังจากราคาหลุดลงมา
แนวรับ-แนวต้านสำคัญ: | Timeframe | แนวรับ | แนวต้าน | |---|---|---| | Day | EMA 50, EMA 200, บริเวณ 96,000-98,000 (Volume Profile), 85,724.7 | 109,998.9 (High เดิม) | | 4H | EMA 50, EMA 200, บริเวณ 96,000-98,000 (Volume Profile, Equilibrium), 89,037.0 | 109,998.9 (EQH, High เดิม) | | 15m | 95,200 (Low ล่าสุด), 94,707.4 (Low ก่อนหน้า) | EMA 50, EMA 200, บริเวณ 96,000, 96,807.8, 97,000-97,200 |
กลยุทธ์ (BTCUSDT): * Wait & See (ทางเลือกที่ดีที่สุดในตอนนี้): * เนื่องจาก TF15 ขัดแย้งกับ TF Day & 4H อย่างชัดเจน การ "รอ" ให้ตลาดเฉลยทิศทางที่ชัดเจนกว่านี้ เป็นทางเลือกที่ปลอดภัยที่สุด * สังเกตพฤติกรรมราคา (Price Action) บริเวณแนวรับ-แนวต้านใน TF15 * Buy on Dip (Day, 4H) - ต้องระมัดระวังอย่างสูง: * สำหรับนักลงทุนระยะกลาง-ยาว ที่เชื่อมั่นในแนวโน้มขาขึ้น * เงื่อนไข: ต้องรอสัญญาณการกลับตัวของราคาใน TF15 ก่อน เช่น * การ Breakout แนวต้านย่อยๆ พร้อม Volume * การเปลี่ยน Money Flow (LuxAlgo) เป็นสีเขียว (ถ้ามี) * การเกิด Bullish Candlestick Patterns * จุดเข้า: บริเวณ EMA 50/200 ของ TF Day หรือ 4H, หรือบริเวณแนวรับอื่นๆ ที่มีนัยสำคัญ * Stop Loss: ต่ำกว่า Low ล่าสุดของ TF15 หรือต่ำกว่าแนวรับที่เข้าซื้อ * Short (15, ความเสี่ยงสูงมาก): * สำหรับนักเก็งกำไรระยะสั้น ที่รับความเสี่ยงได้สูง * เงื่อนไข: ราคาไม่สามารถกลับขึ้นไปยืนเหนือ EMA ของ TF15 ได้ * จุดเข้า: บริเวณ EMA ของ TF15 หรือแนวต้านอื่นๆ * Stop Loss: เหนือ High ล่าสุดของ TF15 หรือเหนือแนวต้านที่เข้า Short
คำแนะนำ: * ความขัดแย้งของ Timeframes: การที่ TF15 ขัดแย้งกับ TF Day & 4H เป็นสิ่งที่ต้องระวังอย่างมาก * Volume: การ Breakout หรือ Breakdown ใดๆ ควรมี Volume สนับสนุน เพื่อยืนยันความน่าเชื่อถือ * Risk Management: สำคัญที่สุด ไม่ว่าจะเลือกกลยุทธ์ใด ต้องมีการบริหารความเสี่ยงที่ดี (ตั้ง Stop Loss, ไม่ Overtrade) * ข่าวสาร: ติดตามข่าวสารที่อาจส่งผลกระทบต่อราคา Bitcoin
สรุป: สถานการณ์ของ BTCUSDT ตอนนี้ค่อนข้างซับซ้อนและมีความเสี่ยงสูง การ "รอ" อาจเป็นทางเลือกที่ดีที่สุดสำหรับนักลงทุนส่วนใหญ่ จนกว่าจะเห็นสัญญาณที่ชัดเจนมากขึ้นค่ะ
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-
 @ d360efec:14907b5f
2025-02-12 05:26:39
@ d360efec:14907b5f
2025-02-12 05:26:39ภาพรวม LUNCUSDT (OKX):
LUNCUSDT กำลังพยายามฟื้นตัวจากแนวโน้มขาลงระยะยาว แต่ยังคงมีความผันผวนและมีความเสี่ยงสูง แนวโน้มระยะกลางถึงยาว (TF Day & 4H) เริ่มมีสัญญาณบวกของการกลับตัวเป็นขาขึ้น (Early Uptrend) หลังจากราคา Breakout EMA 50 ใน TF Day และเกิด Golden Cross อย่างไรก็ตาม ในระยะสั้นมาก (TF15) กลับแสดงถึงความอ่อนแอและมีการปรับฐานลงมา


แนวโน้ม:
- TF Day: เริ่มเป็นขาขึ้น (Early Uptrend) – ราคา Breakout EMA 50 และเกิด Golden Cross, Money Flow เป็นบวก
- TF4H: เริ่มเป็นขาขึ้น (Early Uptrend) – ราคา Breakout EMA 50, มีการพักตัวลงมาทดสอบ EMA 50, Money Flow เริ่มไม่แน่นอน
- TF15: แกว่งตัวออกข้าง (Sideways) หลังจากร่วงลง – ราคาอยู่ใต้ EMA, โครงสร้างราคาเป็น Lower Highs/Lows, Money Flow เป็นลบ
โครงสร้างราคา (SMC):
- TF Day: มี Break of Structure (BOS) ด้านบน, เริ่มเห็น Higher Highs (HH) และ Higher Lows (HL)
- TF4H: มี BOS ด้านบน, เริ่มเห็น HH/HL (แต่ไม่ชัดเจน), มี Equal Highs (EQH) และ Equal Lows (EQL)
- TF15: มี BOS ด้านล่าง, มี Change of Character (CHoCH) ทั้งบนและล่าง, เริ่มเห็น Lower Highs (LH) และ Lower Lows (LL)
Money Flow (LuxAlgo):
- TF Day: แรงซื้อแข็งแกร่ง (ไม่มีภาพ แต่จากการวิเคราะห์ก่อนหน้า)
- TF4H: แรงซื้อและแรงขายพอๆ กัน, เริ่มมีแรงขายเข้ามา
- TF15: แรงขายมีมากกว่าแรงซื้อ
EMA (Exponential Moving Average):
- TF Day: EMA 50 & 200 เป็นแนวรับ
- TF4H: EMA 50 เป็นแนวรับที่กำลังถูกทดสอบ, EMA 200 เป็นแนวต้าน
- TF15: EMA 50 & 200 กลายเป็นแนวต้าน
แนวรับ-แนวต้านสำคัญ:
| Timeframe | แนวรับ | แนวต้าน | | :-------- | :------------------------------------------------------------------------ | :------------------------------------------------------------------------------------------- | | Day | EMA 50 (0.00010000), EMA 200 (0.00008000), 0.00006000-0.00007000 | 0.00017953 (High ล่าสุด), 0.00014000 (Volume Profile) | | 4H | EMA 50 (ประมาณ 0.00007000), 0.00006000-0.00007000, Equilibrium | EMA 200 (0.00008000), 0.00008132, 0.00010000-0.00012000 (EQH) | | 15m | 0.00007300 (EQL, Volume Profile) | EMA 50, EMA 200, 0.00007531 (EQH), 0.00007636 (EQH, High ก่อนหน้า) |
กลยุทธ์ (LUNCUSDT):
- Wait & See (ทางเลือกที่ดีที่สุด):
- เนื่องจาก TF15 ขัดแย้งกับ TF Day & 4H และ TF4H ก็เริ่มแสดงสัญญาณอ่อนแรง การ "รอ" ให้ตลาดแสดงทิศทางที่ชัดเจนกว่านี้ จะเป็นทางเลือกที่ปลอดภัยที่สุด
- สังเกตพฤติกรรมราคา (Price Action) บริเวณแนวรับ-แนวต้านใน TF15 และ TF4H
- Buy on Dip (Day, 4H) - ความเสี่ยงสูงมาก ต้องระมัดระวังเป็นพิเศษ:
- สำหรับนักลงทุนระยะกลาง-ยาว ที่เชื่อมั่นในการกลับตัวของ LUNC (แต่ต้องยอมรับความเสี่ยงได้สูงมาก)
- เงื่อนไข: ต้องรอสัญญาณการกลับตัวของราคาใน TF15 ก่อน เช่น
- การ Breakout แนวต้านย่อยๆ พร้อม Volume
- การเปลี่ยน Money Flow (LuxAlgo) เป็นสีเขียว
- การเกิด Bullish Candlestick Patterns
- จุดเข้า (Day): EMA 50 (0.00010000), EMA 200 (0.00008000) ต้องดู TF15 ประกอบ
- จุดเข้า (4H): EMA 50 (ประมาณ 0.00007000) ต้องดู TF15 ประกอบ
- Stop Loss: ต่ำกว่า Low ล่าสุดของ TF15 หรือต่ำกว่าแนวรับที่เข้าซื้อ
- Short (15, ความเสี่ยงสูงมาก):
- สำหรับนักเก็งกำไรระยะสั้น ที่รับความเสี่ยงได้สูงมาก
- เงื่อนไข: ราคาไม่สามารถกลับขึ้นไปยืนเหนือ EMA ของ TF15 ได้
- จุดเข้า: บริเวณ EMA ของ TF15 หรือแนวต้านอื่นๆ
- Stop Loss: เหนือ High ล่าสุดของ TF15 หรือเหนือแนวต้านที่เข้า Short
คำแนะนำ (เน้นย้ำ):
- ความขัดแย้งของ Timeframes: สถานการณ์ของ LUNCUSDT ตอนนี้มีความขัดแย้งกันสูงมากระหว่าง Timeframes และมีความเสี่ยงสูงกว่า XRP และ BTC
- Money Flow: Money Flow ใน TF15 เป็นลบ และใน TF4H ก็เริ่มไม่แน่นอน
- LUNC เป็นเหรียญ High Risk: มีความผันผวนสูงมาก และอาจมีการเปลี่ยนแปลงอย่างรวดเร็ว
- ถ้าไม่แน่ใจ อย่าเพิ่งเข้าเทรด: รอสัญญาณที่ชัดเจนกว่านี้ หรือเลือกเทรดเหรียญอื่นที่มีความเสี่ยงน้อยกว่า
- Risk Management: สำคัญที่สุด ไม่ว่าจะเลือกกลยุทธ์ใด ต้องมีการบริหารความเสี่ยงที่ดี (ตั้ง Stop Loss, ไม่ Overtrade, กระจายความเสี่ยง)
สรุป: LUNCUSDT กำลังอยู่ในช่วงเวลาที่ยากลำบากและมีความเสี่ยงสูงมาก การตัดสินใจที่ผิดพลาดอาจนำไปสู่การขาดทุนได้ ควรพิจารณาอย่างรอบคอบก่อนเข้าเทรดทุกครั้ง และ "รอ" อาจเป็นทางเลือกที่ดีที่สุดสำหรับนักลงทุนส่วนใหญ่ค่ะ
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-
 @ d360efec:14907b5f
2025-02-12 04:39:09
@ d360efec:14907b5f
2025-02-12 04:39:09ภาพรวม XRPUSDT :
XRPUSDT กำลังอยู่ในช่วงหัวเลี้ยวหัวต่อ คล้ายกับ BTC แต่มีความอ่อนแอกว่าเล็กน้อย แนวโน้มระยะกลางถึงยาว (TF Day & 4H) เริ่มมีสัญญาณบวกของการเป็นขาขึ้น (Early Uptrend) แต่ในระยะสั้นมาก (TF15) กลับแสดงถึงความอ่อนแอและมีการปรับฐานลงมา


แนวโน้ม:
- TF Day: เริ่มเป็นขาขึ้น (Early Uptrend) – ราคา Breakout EMA 50 ขึ้นมาได้, Money Flow เป็นบวก
- TF4H: เริ่มเป็นขาขึ้น (Early Uptrend) – ราคา Breakout EMA 50, มีการพักตัวลงมาทดสอบ EMA 50, Money Flow เริ่มอ่อนแรง
- TF15: แกว่งตัวลง (Sideways Down) – ราคาหลุด EMA, โครงสร้างราคาเป็น Lower Highs/Lows, Money Flow เป็นลบ
โครงสร้างราคา (SMC):
- TF Day: มี Break of Structure (BOS) ด้านบน, เริ่มเห็น Higher Highs (HH) และ Higher Lows (HL)
- TF4H: มี BOS ด้านบน, เริ่มเห็น HH/HL (แต่ไม่ชัดเจน), มี Equal Highs (EQH) และ Equal Lows (EQL)
- TF15: มี BOS ด้านล่าง, มี Change of Character (CHoCH) ทั้งบนและล่าง, เริ่มเห็น Lower Highs (LH) และ Lower Lows (LL)
Money Flow (LuxAlgo):
- TF Day: แรงซื้อแข็งแกร่ง
- TF4H: แรงซื้อเริ่มอ่อนแรงลง, มีแรงขายเข้ามา
- TF15: แรงขายมีมากกว่าแรงซื้อ
EMA (Exponential Moving Average):
- TF Day: EMA 50 & 200 เป็นแนวรับ
- TF4H: EMA 50 เป็นแนวรับที่กำลังถูกทดสอบ, EMA 200 เป็นแนวรับถัดไป
- TF15: EMA 50 & 200 กลายเป็นแนวต้าน
แนวรับ-แนวต้านสำคัญ:
| Timeframe | แนวรับ | แนวต้าน | | :-------- | :------------------------------------------------------------------------ | :-------------------------------------------------------------------- | | Day | EMA 50 (1.56), EMA 200 (1.08), Low ก่อนหน้า | 2.4450 (High ล่าสุด), 3.00-3.20 (EQH), 3.4049 | | 4H | EMA 50 (ประมาณ 2.20), EMA 200, 2.10-2.20 (EQL), 1.7820 | 2.4427, 2.3987, 3.00-3.20 (EQH), 3.4049 | | 15m | 2.38 (EQL, Volume Profile), 2.3274 | EMA 50, EMA 200, 2.4196, Equilibrium (2.44), 2.44-2.48 (EQH) |
กลยุทธ์ (XRPUSDT):
- Wait & See (ทางเลือกที่ดีที่สุด):
- เนื่องจาก TF15 ขัดแย้งกับ TF Day & 4H อย่างชัดเจน และ TF4H ก็เริ่มแสดงสัญญาณอ่อนแรง การ "รอ" ให้ตลาดแสดงทิศทางที่ชัดเจนกว่านี้ จะเป็นทางเลือกที่ปลอดภัยที่สุด
- สังเกตพฤติกรรมราคา (Price Action) บริเวณแนวรับ-แนวต้านใน TF15 และ TF4H
- Buy on Dip (Day, 4H) - ความเสี่ยงสูงมาก ต้องระมัดระวังเป็นพิเศษ:
- สำหรับนักลงทุนระยะกลาง-ยาว ที่เชื่อมั่นในแนวโน้มขาขึ้น (แต่ต้องยอมรับความเสี่ยงได้สูง)
- เงื่อนไข: ต้องรอสัญญาณการกลับตัวของราคาใน TF15 ก่อน เช่น
- การ Breakout แนวต้านย่อยๆ พร้อม Volume
- การเปลี่ยน Money Flow (LuxAlgo) เป็นสีเขียว
- การเกิด Bullish Candlestick Patterns
- จุดเข้า (Day): EMA 50 (1.56), EMA 200 (1.08) ต้องดู TF15 ประกอบ
- จุดเข้า (4H): EMA 50 (2.20), บริเวณ EQL (2.10-2.20) ต้องดู TF15 ประกอบ
- Stop Loss: ต่ำกว่า Low ล่าสุดของ TF15 หรือต่ำกว่าแนวรับที่เข้าซื้อ
- Short (15, ความเสี่ยงสูงมาก):
- สำหรับนักเก็งกำไรระยะสั้น ที่รับความเสี่ยงได้สูงมาก
- เงื่อนไข: ราคาไม่สามารถกลับขึ้นไปยืนเหนือ EMA ของ TF15 ได้
- จุดเข้า: บริเวณ EMA ของ TF15 หรือแนวต้านอื่นๆ
- Stop Loss: เหนือ High ล่าสุดของ TF15 หรือเหนือแนวต้านที่เข้า Short
คำแนะนำ (เน้นย้ำ):
- ความขัดแย้งของ Timeframes: สถานการณ์ของ XRPUSDT ตอนนี้มีความขัดแย้งกันสูงมากระหว่าง Timeframes
- Money Flow: Money Flow ใน TF15 เป็นลบ และใน TF4H ก็เริ่มอ่อนแรง
- EMA 50 (TF4H): เป็นจุดชี้ชะตา ถ้าหลุด แนวโน้มขาขึ้นระยะกลางอาจเสีย
- ถ้าไม่แน่ใจ อย่าเพิ่งเข้าเทรด: รอสัญญาณที่ชัดเจนกว่านี้ หรือเลือกเทรดเหรียญอื่นที่มีความเสี่ยงน้อยกว่า
สรุป: XRPUSDT กำลังอยู่ในช่วงเวลาที่ยากลำบากและมีความเสี่ยงสูง การตัดสินใจที่ผิดพลาดอาจนำไปสู่การขาดทุนได้ ควรพิจารณาอย่างรอบคอบก่อนเข้าเทรดทุกครั้งค่ะ
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-
 @ d360efec:14907b5f
2025-02-12 03:42:09
@ d360efec:14907b5f
2025-02-12 03:42:09บทที่ 1: การเดินทางของนักเวทย์สาว ข้าคือ อาเรีย นักเวทย์ฝึกหัดผู้เดินทางมาจากดินแดนอันไกลโพ้น ข้าได้ยินเรื่องราวของอาณาจักรไทย ที่ซึ่งมีปัญหาเกี่ยวกับ "แรงงานเงา" ซึ่งเป็นกลุ่มคนจากอีกดินแดนหนึ่งที่เข้ามาทำงานในอาณาจักรแห่งนี้ ข้าตัดสินใจที่จะเดินทางมายังอาณาจักรไทย เพื่อศึกษาเรื่องราวเหล่านี้ และหาทางแก้ไขปัญหา

บทที่ 2: การพบปะกับผู้คน เมื่อข้ามาถึงอาณาจักรไทย ข้าได้พบกับผู้คนมากมาย ทั้งชาวไทยและชาวพม่า ข้าได้ฟังเรื่องราวของพวกเขา ทั้งความยากลำบากในการทำงาน การถูกกดขี่ค่าแรง และความหวังที่จะมีชีวิตที่ดีขึ้น ข้าได้เห็นถึงความขยันและอดทนของพวกเขา แต่ก็มีความขัดแย้งและความเข้าใจผิดเกิดขึ้นระหว่างคนทั้งสองกลุ่ม

บทที่ 3: การไขปริศนา ข้าเริ่มสืบหาความจริงเกี่ยวกับเรื่องราวเหล่านี้ และได้พบว่ามีกลุ่มคนบางกลุ่มที่ต้องการใช้ประโยชน์จากแรงงานเงาม โดยการกดขี่ค่าแรงและแสวงหาผลประโยชน์ ข้ายังได้เรียนรู้ว่าอาณาจักรไทยกำลังเผชิญกับปัญหาการขาดแคลนแรงงาน และจำเป็นต้องพึ่งพาแรงงานเงา

บทที่ 4: การตัดสินใจ ข้าได้คิดทบทวนเรื่องราวทั้งหมด และตัดสินใจที่จะใช้เวทย์มนตร์ของข้า เพื่อช่วยเหลือผู้คนเหล่านั้น ข้าต้องการที่จะสร้างความเข้าใจและความเท่าเทียมกันระหว่างคนทุกกลุ่ม และทำให้อาณาจักรไทยเป็นสถานที่ที่ทุกคนสามารถอยู่ร่วมกันได้อย่างมีความสุข

บทที่ 5: การผจญภัย การเดินทางของข้ายังไม่จบสิ้น ข้ายังคงต้องเผชิญกับอุปสรรคและความท้าทายอีกมากมาย แต่ข้าเชื่อมั่นว่าด้วยความมุ่งมั่นและความพยายามของข้า ข้าจะสามารถสร้างความเปลี่ยนแปลงให้กับอาณาจักรไทยแห่งนี้ได้

บทสรุป
เรื่องราวของอาเรีย นักเวทย์สาวผู้เดินทางมาเพื่อแก้ไขปัญหาแรงงานเงาในอาณาจักรไทย เป็นเรื่องราวที่สะท้อนให้เห็นถึงปัญหาที่เกิดขึ้นในสังคมของเรา การกดขี่ค่าแรง การแบ่งแยกชนชั้น และการแสวงหาผลประโยชน์จากผู้อื่น
เราทุกคนสามารถเป็นเหมือนอาเรียได้ โดยการลุกขึ้นมาต่อสู้เพื่อความถูกต้องและความเท่าเทียมกัน และสร้างสังคมที่ทุกคนสามารถอยู่ร่วมกันได้อย่างมีความสุข
-
 @ d360efec:14907b5f
2025-02-11 05:46:56
@ d360efec:14907b5f
2025-02-11 05:46:56(1) TF Day (รายวัน): - แนวโน้ม: ขาขึ้น (Uptrend) ชัดเจน - SMC: HH และ HL ต่อเนื่อง - แนวรับ: EMA 50 (ประมาณ 90,000), EMA 200 (ประมาณ 80,000) - แนวต้าน: 109,998.9 (High เดิม) - Money Flow (LuxAlgo): - ส่วนใหญ่เป็นสีเขียว: แสดงว่าโดยรวมแล้วแรงซื้อยังมีอิทธิพลเหนือกว่า - มีสีแดงแทรกบ้าง: บ่งบอกว่ามีการขายทำกำไรออกมาบ้าง แต่ไม่มากพอที่จะเปลี่ยนแนวโน้มหลัก - มีสีเขียวแท่งใหญ่ต่อเนื่อง: เกิดขึ้นในช่วงที่ราคามีการปรับตัวขึ้นอย่างมีนัยยะสำคัญ สรุป: ขาขึ้นแข็งแกร่ง Buy on Dip ที่ EMA 50/200

(2) TF4H (4 ชั่วโมง): - แนวโน้ม: ขาขึ้น (Uptrend) ชัดเจน - SMC: HH และ HL, มี Pullback แต่ไม่เสียโครงสร้าง - แนวรับ: EMA 50, EMA 200, Equilibrium (ประมาณ 98,000) - แนวต้าน: 109,998.9 - Money Flow (LuxAlgo): แรงซื้อยังคงมีมากกว่า, มีขายทำกำไรบ้าง สรุป: ขาขึ้น พักตัวเพื่อไปต่อ Buy on Dip

(3) TF15 (15 นาที): - แนวโน้ม: ขาขึ้น (Uptrend) แต่แกว่งตัวในกรอบ (Consolidation) - SMC: Accumulation, มี EQH/EQL, CHoCH ทั้งบนและล่าง - แนวรับ: 97,000-97,200, EMA, 96,800 - แนวต้าน: 98,000-98,378.4 - Money Flow (LuxAlgo): แรงซื้อยังคงมี แต่มีแรงขายทำกำไร สรุป: ขาขึ้นระยะสั้น แต่ผันผวน Range Trading หรือ Breakout Trading (เน้น Buy)

กลยุทธ์: 1.Buy on Dip (หลัก): - TF Day: รอใกล้ EMA 50/200 - TF4H: รอใกล้ EMA หรือ Equilibrium
2.Breakout (TF15): รอ Breakout 98,000-98,378.4 พร้อม Volume
3.Range (TF15, เสี่ยง): เล่นสั้นในกรอบ 97,000-98,000 (ระวัง False Breakout)
4.ไม่ Short: ขัดกับแนวโน้มหลัก
ข้อควรระวัง: - ความผันผวน: ตลาดคริปโตฯ มีความผันผวนสูง - ข่าวสาร/ปัจจัยพื้นฐาน: ติดตามข่าวสารอย่างใกล้ชิด - Stop Loss: จำเป็นต้องตั้ง Stop Loss ทุกครั้งที่เข้าเทรด - TF15: ระวัง False Breakout และ Volume ที่ไม่สอดคล้อง
Money Flow (LuxAlgo) สรุป: - TF Day: ยืนยันแนวโน้มขาขึ้นโดยรวม แรงซื้อยังมีอิทธิพล - TF4H: ยืนยันแนวโน้มขาขึ้น แรงซื้อยังคงมีมากกว่า - TF15: แรงซื้อยังมี แต่เริ่มมีแรงขายทำกำไร ทำให้ราคาแกว่งตัว
คำแนะนำเพิ่มเติม: - Volume: ควรให้ความสำคัญกับ Volume ในการ Breakout หรือ Breakout - Risk Management: บริหารความเสี่ยงให้ดี อย่า Overtrade
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-
 @ d360efec:14907b5f
2025-02-11 05:43:45
@ d360efec:14907b5f
2025-02-11 05:43:45(1) TF Day (รายวัน): - แนวโน้ม: เริ่มเป็นขาขึ้น (Early Uptrend) หลังจาก Breakout EMA 50 - SMC: BOS ด้านบน (Breakout EMA 50), เริ่มเห็น HH/HL (แต่ยังไม่ชัดเจนเท่า BTC) - แนวรับ: EMA 50 (1.5615), EMA 200 (1.0857), 0.7289-0.8479 - แนวต้าน: 2.4450 (High ล่าสุด), 3.00-3.20 (EQH), 3.4049 (High ก่อนหน้า) - Money Flow (LuxAlgo): แรงซื้อแข็งแกร่ง ชนะแรงขายชัดเจน - Volume Profile: หนาแน่นที่ EMA 50 - กลยุทธ์: Buy on Dip (ความเสี่ยงปานกลาง) หรือรอ Breakout 2.4450

(2) TF4H (4 ชั่วโมง): - แนวโน้ม: ขาขึ้น (ระยะกลาง), พักตัว (ระยะสั้น) - SMC: BOS ด้านบน, เริ่มเห็น HH/HL, มี EQH (3.00-3.20) และ EQL (2.10-2.20) - แนวรับ: EMA 50 (2.20), EMA 200 (1.80), 2.10-2.20 (EQL), 1.7820 - แนวต้าน: 2.4427, 3.00-3.20 (EQH), 3.4049 - Money Flow (LuxAlgo): แรงซื้อยังมี แต่เริ่มอ่อนแรงลง มีขายทำกำไร - Volume Profile: หนาแน่นที่ EMA 50 - กลยุทธ์: Buy on Dip ใกล้ EMA 50 หรือ EQL, รอ Breakout 2.4427

(3) TF15 (15 นาที): - แนวโน้ม: แกว่งตัวในกรอบ (Sideways) - SMC: Accumulation/Distribution, EQH (2.44-2.48), EQL (2.40-2.42), CHoCH ทั้งบนและล่าง - แนวรับ: 2.40-2.42 (EQL, EMA), Equilibrium (2.38) - แนวต้าน: 2.44-2.48 (EQH), 2.50 - Money Flow (LuxAlgo): แรงซื้อและแรงขายพอๆ กัน, Volume ไม่สูง - Volume Profile: หนาแน่นที่ 2.40-2.42 - กลยุทธ์: Range Trading (เสี่ยง) หรือ Breakout Trading (เน้น Buy)

สรุปกลยุทธ์สำหรับ XRPUSDT: 1.Buy on Dip (กลยุทธ์หลัก): - TF Day: รอราคาย่อตัวลงมาใกล้ EMA 50 (ประมาณ 1.56) หรือ EMA 200 (ประมาณ 1.08) - TF4H: รอราคาย่อตัวลงมาใกล้ EMA 50 (ประมาณ 2.20) หรือบริเวณ EQL (2.10-2.20)
2.Breakout Trading (TF15, เสี่ยงน้อยกว่า Range Trading): - รอราคา Breakout แนวต้าน 2.44-2.48 (EQH ใน TF15) อย่างแข็งแกร่ง พร้อม Volume ยืนยัน แล้วค่อยพิจารณา Buy Stop
3.Range Trading (TF15, ความเสี่ยงสูง): - เล่นสั้นๆ ในกรอบ 2.40-2.48 (ซื้อแนวรับ-ขายแนวต้าน) ต้องระวัง False Breakout อย่างมาก
4.ไม่แนะนำให้ Short: - ขัดกับแนวโน้มหลักใน TF Day และ TF4H รวมถึง Money Flow ที่แสดงแรงซื้อ
ข้อควรระวัง: - ความผันผวน: XRP มีความผันผวนสูง - ข่าวสาร: ติดตามข่าวสารเกี่ยวกับ Ripple และคดีความกับ SEC - False Breakout (TF15): ระวังการ Breakout หลอก โดยเฉพาะในสภาวะที่ Volume ไม่สูง - Stop Loss: ต้องตั้ง Stop Loss ทุกครั้งที่เข้าเทรด เพื่อจำกัดความเสี่ยง
คำแนะนำ: - XRP ยังตามหลัง BTC การเข้าซื้อควรรอสัญญาณที่ชัดเจน - TF Day และ TF4H เป็นตัวกำหนดแนวโน้มหลัก - TF15 ใช้สำหรับหาจังหวะเข้า-ออกระยะสั้น - บริหารความเสี่ยง (Risk Management) เป็นสิ่งสำคัญที่สุด
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ
-
 @ d360efec:14907b5f
2025-02-11 05:39:54
@ d360efec:14907b5f
2025-02-11 05:39:54ภาพรวม LUNCUSDT:
LUNCUSDT กำลังแสดงสัญญาณของการฟื้นตัว (Potential Reversal) จากแนวโน้มขาลงระยะยาว โดยมีปัจจัยสนับสนุนหลักคือการ Breakout EMA 50 ใน TF Day และการเกิด Golden Cross (EMA 50 ตัด EMA 200 ขึ้น) อย่างไรก็ตาม การฟื้นตัวนี้ยังอยู่ในช่วงเริ่มต้น และยังคงมีความผันผวนและแรงขายทำกำไรอยู่บ้าง
แนวโน้ม: - TF Day: แนวโน้มขาขึ้น (Early Stage) – บ่งชี้ถึงโอกาสในการกลับตัวระยะยาว - TF4H: แนวโน้มขาขึ้น (ระยะกลาง) – ยืนยันแนวโน้มขาขึ้น แต่มีการพักตัวระยะสั้น - TF15: แนวโน้มแกว่งตัวขึ้น (Sideways Up) – แสดงถึงการต่อสู้ระหว่างแรงซื้อและแรงขายในระยะสั้น
โครงสร้างราคา (SMC): - TF Day: มี Break of Structure (BOS) ด้านบน, เริ่มเห็น Higher Highs (HH) และ Higher Lows (HL) - TF4H: มี BOS ด้านบน, เริ่มเห็น HH/HL, มี Equal Highs (EQH) เป็นแนวต้าน - TF15: มี BOS ด้านบน, มี Change of Character (CHoCH) ด้านบน, มี EQH และ Equal Lows (EQL)
Money Flow (LuxAlgo): - TF Day: แรงซื้อแข็งแกร่งอย่างชัดเจน - TF4H: แรงซื้อและแรงขายค่อนข้างสมดุล มีการขายทำกำไร - TF15: แรงซื้อและแรงขายพอๆ กัน แต่แรงซื้อเริ่มกลับเข้ามา
แนวรับ-แนวต้านสำคัญ: - Timeframe Day - แนวรับ EMA 50 (0.00010000), EMA 200 (0.00008000), 0.00006000-0.00007000 - แนวต้าน 0.00017953 (High ล่าสุด), 0.00014000 (Volume Profile) - Timeframe 4H - แนวรับ EMA 50 (0.00007000), EMA 200 (0.00008000), Equilibrium (0.00008500), 0.00006000 - แนวต้าน 0.00008132 (High ล่าสุด), 0.00010000 (EQH), 0.00010755 (High ก่อนหน้า) - Timeframe 15m - แนวรับ EMA 50, EMA 200, 0.00007300-0.00007400, Equilibrium (0.00007100) - แนวต้าน 0.00007636 (High ล่าสุด), EQH (0.00007600)
กลยุทธ์: 1.Buy on Dip (กลยุทธ์หลัก): - Day/4H: รอราคาย่อตัวลงมาใกล้แนวรับสำคัญ (EMA, Equilibrium) เป็นจุดที่น่าสนใจในการเข้าซื้อ โดยพิจารณาจากสัญญาณอื่นๆ ประกอบ (เช่น Volume, Candlestick Patterns) 2.Breakout Trading: - Day: รอ Breakout แนวต้าน 0.00014000 หรือ 0.00017953 พร้อม Volume ยืนยัน - 15: รอ Breakout แนวต้าน 0.00007636 พร้อม Volume ยืนยัน 3.Range Trading (TF15, ความเสี่ยงสูง): ไม่แนะนำสำหรับมือใหม่ เล่นสั้นๆ ในกรอบแนวรับ-แนวต้านของ TF15 (ต้องระวัง False Breakout อย่างมาก) 4.ไม่แนะนำให้ Short: ขัดกับสัญญาณการกลับตัวใน TF Day และ 4H
ข้อควรระวัง: - LUNC เป็นเหรียญ High Risk: มีความผันผวนสูงมาก - ข่าวสาร: ติดตามข่าวสารเกี่ยวกับ Terra Luna Classic อย่างใกล้ชิด - Stop Loss: ต้องตั้ง Stop Loss ทุกครั้งที่เข้าเทรด เพื่อจำกัดความเสี่ยง
คำแนะนำ: - LUNC มีความเสี่ยงสูงกว่า BTC และ XRP - ควรกระจายความเสี่ยง (Diversification) อย่าลงทุนใน LUNC เพียงอย่างเดียว - ลงทุนในสัดส่วนที่น้อย (เมื่อเทียบกับพอร์ตการลงทุนทั้งหมด) - ถ้าไม่แน่ใจ ให้รอสัญญาณที่ชัดเจนกว่านี้ก่อน (เช่น การ Breakout แนวต้านสำคัญพร้อม Volume)
Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัว ไม่ถือเป็นคำแนะนำในการลงทุน ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบ



-
 @ daa41bed:88f54153
2025-02-09 16:50:04
@ daa41bed:88f54153
2025-02-09 16:50:04There has been a good bit of discussion on Nostr over the past few days about the merits of zaps as a method of engaging with notes, so after writing a rather lengthy article on the pros of a strategic Bitcoin reserve, I wanted to take some time to chime in on the much more fun topic of digital engagement.
Let's begin by defining a couple of things:
Nostr is a decentralized, censorship-resistance protocol whose current biggest use case is social media (think Twitter/X). Instead of relying on company servers, it relies on relays that anyone can spin up and own their own content. Its use cases are much bigger, though, and this article is hosted on my own relay, using my own Nostr relay as an example.
Zap is a tip or donation denominated in sats (small units of Bitcoin) sent from one user to another. This is generally done directly over the Lightning Network but is increasingly using Cashu tokens. For the sake of this discussion, how you transmit/receive zaps will be irrelevant, so don't worry if you don't know what Lightning or Cashu are.
If we look at how users engage with posts and follows/followers on platforms like Twitter, Facebook, etc., it becomes evident that traditional social media thrives on engagement farming. The more outrageous a post, the more likely it will get a reaction. We see a version of this on more visual social platforms like YouTube and TikTok that use carefully crafted thumbnail images to grab the user's attention to click the video. If you'd like to dive deep into the psychology and science behind social media engagement, let me know, and I'd be happy to follow up with another article.
In this user engagement model, a user is given the option to comment or like the original post, or share it among their followers to increase its signal. They receive no value from engaging with the content aside from the dopamine hit of the original experience or having their comment liked back by whatever influencer they provide value to. Ad revenue flows to the content creator. Clout flows to the content creator. Sales revenue from merch and content placement flows to the content creator. We call this a linear economy -- the idea that resources get created, used up, then thrown away. Users create content and farm as much engagement as possible, then the content is forgotten within a few hours as they move on to the next piece of content to be farmed.
What if there were a simple way to give value back to those who engage with your content? By implementing some value-for-value model -- a circular economy. Enter zaps.

Unlike traditional social media platforms, Nostr does not actively use algorithms to determine what content is popular, nor does it push content created for active user engagement to the top of a user's timeline. Yes, there are "trending" and "most zapped" timelines that users can choose to use as their default, but these use relatively straightforward engagement metrics to rank posts for these timelines.
That is not to say that we may not see clients actively seeking to refine timeline algorithms for specific metrics. Still, the beauty of having an open protocol with media that is controlled solely by its users is that users who begin to see their timeline gamed towards specific algorithms can choose to move to another client, and for those who are more tech-savvy, they can opt to run their own relays or create their own clients with personalized algorithms and web of trust scoring systems.
Zaps enable the means to create a new type of social media economy in which creators can earn for creating content and users can earn by actively engaging with it. Like and reposting content is relatively frictionless and costs nothing but a simple button tap. Zaps provide active engagement because they signal to your followers and those of the content creator that this post has genuine value, quite literally in the form of money—sats.

I have seen some comments on Nostr claiming that removing likes and reactions is for wealthy people who can afford to send zaps and that the majority of people in the US and around the world do not have the time or money to zap because they have better things to spend their money like feeding their families and paying their bills. While at face value, these may seem like valid arguments, they, unfortunately, represent the brainwashed, defeatist attitude that our current economic (and, by extension, social media) systems aim to instill in all of us to continue extracting value from our lives.
Imagine now, if those people dedicating their own time (time = money) to mine pity points on social media would instead spend that time with genuine value creation by posting content that is meaningful to cultural discussions. Imagine if, instead of complaining that their posts get no zaps and going on a tirade about how much of a victim they are, they would empower themselves to take control of their content and give value back to the world; where would that leave us? How much value could be created on a nascent platform such as Nostr, and how quickly could it overtake other platforms?
Other users argue about user experience and that additional friction (i.e., zaps) leads to lower engagement, as proven by decades of studies on user interaction. While the added friction may turn some users away, does that necessarily provide less value? I argue quite the opposite. You haven't made a few sats from zaps with your content? Can't afford to send some sats to a wallet for zapping? How about using the most excellent available resource and spending 10 seconds of your time to leave a comment? Likes and reactions are valueless transactions. Social media's real value derives from providing monetary compensation and actively engaging in a conversation with posts you find interesting or thought-provoking. Remember when humans thrived on conversation and discussion for entertainment instead of simply being an onlooker of someone else's life?
If you've made it this far, my only request is this: try only zapping and commenting as a method of engagement for two weeks. Sure, you may end up liking a post here and there, but be more mindful of how you interact with the world and break yourself from blind instinct. You'll thank me later.

-
 @ d360efec:14907b5f
2025-02-07 09:42:54
@ d360efec:14907b5f
2025-02-07 09:42:54ณ ดินแดนอันไกลโพ้น ปรากฏดันเจี้ยนลึกลับไร้ก้นบึ้ง นามว่า "ตลาดการเก็งกำไร" ประตูทางเข้าเปล่งประกายล่อตาล่อใจ แต่มักถูกปกคลุมด้วยหมอกแห่งความไม่แน่นอน
คำจารึกโบราณ แกะสลักเหนือประตูทางเข้า เตือนสติผู้มาเยือน: "ผู้ใดเข้าล้วนมิอาจหวนคืน..." เฉกเช่นสำนวนโบราณที่กล่าวขาน "คนในมิอาจออก คนนอกมิต้องการย่างกราย"
ภาพที่ปรากฎตรงหน้า คือชายหนุ่มผู้หาญกล้า กำลังจะก้าวเข้าสู่ประตูดันเจี้ยน เหนือประตูมีป้ายขนาดมหึมาสลักคำว่า "Trading" สัญลักษณ์แห่งโลกการลงทุน การเก็งกำไร ไม่ว่าจะเป็น หุ้น, ฟอเร็กซ์, คริปโต ล้วนเป็นมอนสเตอร์ที่สถิตอยู่ในนี้
การจะพิชิตดันเจี้ยนนี้ได้นั้น หาใช่เรื่องง่าย ภารกิจแรกคือการกำจัดปีศาจ"นักพนัน" ที่สิงอยู่ในจิตใจของผู้กล้าทุกคน ปีศาจตนนี้ร้ายกาจยิ่งนัก แต่มิใช่ว่าไร้ทางปราบ หากท่านผู้กล้าปรารถนาจะหลุดพ้นจากวงจรอุบาทว์นี้ จงใช้วิธีเหล่านี้เถิด
- เข้าใจว่าการพนันคือกับดัก
ปีศาจพนันมักล่อลวงด้วยภาพลวงตาแห่งชัยชนะเพียงชั่วครู่ แต่แท้จริงแล้ว มันถูกออกแบบมาเพื่อสูบเลือดสูบเนื้อจากเหล่าผู้กล้าในระยะยาว จงจำไว้ว่าการพนันมิใช่หนทางสู่ความร่ำรวย แต่เป็นเส้นทางสู่หุบเหวแห่งความสิ้นเนื้อประดาตัว
- เปลี่ยนมุมมองเกี่ยวกับเหรียญทอง
จงมองเหรียญทองที่ท่านมีมิใช่แค่ตัวเลข แต่เป็น “เวลาและหยาดเหงื่อ” ที่ท่านได้แลกมา หากท่านสูญเสียมันไปเพราะการพนัน มันคือเวลาชีวิตที่หายไปตลอดกาล
- ตัดขาดสิ่งเร้าที่กระตุ้นให้เล่น
• ลบแอปพนัน / ปิดกั้นเว็บไซต์มืด • เลิกติดตามเพจหรือกลุ่มที่เกี่ยวข้อง • เปลี่ยนสหายร่วมทางที่ชักชวนไปสู่ทางเสื่อม
- ใช้กฎ 5 นาที
เมื่อใดที่ความกระหายอยากเล่นครอบงำ จงหยุดยั้งตัวเองไว้ 5 นาที แล้วตรองดูว่า • คราก่อนท่านสูญเสียไปเท่าใด? • หากเล่นแล้วเสียอีก จะรู้สึกเช่นไร? • มีสิ่งใดที่ควรทำมากกว่านี้หรือไม่?
- แสวงหาเส้นทางแห่งการลงทุนที่แท้จริง
แทนที่จะใช้เหรียญทองไปกับการพนัน จงเปลี่ยนเป็นการลงทุนที่มีโอกาสเติบโต เช่น เป็นนักรบแห่งคุณค่า (VI) , เข้าซื้อหุ้นแล้วเก็บมันไว้ในหีบสมบัติ 1 ปี , DCA BTC ดั่งสะสมขุมทรัพย์ทีละน้อย
-
ถามตัวเองว่า “อยากเป็นผู้ชนะ หรือเป็นเหยื่อ?” ผู้ที่ร่ำรวยจากการพนันคือนักลงทุนผู้เปิดบ่อน มิใช่ผู้เล่น หากท่านปรารถนาจะเป็นผู้ชนะ จงเลือกเส้นทางที่ชาญฉลาดกว่า
-
ตั้งเป้าหมายที่ยิ่งใหญ่กว่า
จงตั้งเป้าหมายที่ชัดเจน เช่น สะสมเหรียญทองเพื่อซื้อปราสาท 5 ล้าน หรือหาเงิน 100 ล้าน แล้วจงมุ่งมั่นไปที่มัน การพนันจะทำให้เป้าหมายของท่านล่าช้าลง
📉 เหตุใดดันเจี้ยนแห่งการเทรดจึงเปรียบเสมือนเขาวงกต?
1️⃣ ก้าวเข้ามาง่าย ออกไปยาก
• การเข้าสู่ตลาดการเงินเป็นเรื่องง่ายดาย ใช้เพียงบัญชีเทรดและเงินทุนเพียงเล็กน้อย แต่เมื่อเข้ามาแล้ว จิตวิทยาแห่งการลงทุน และ ความผันผวนของตลาด จะทำให้ยากที่จะออกไป
2️⃣ เส้นทางที่ซับซ้อน
• นักรบมือใหม่มักคิดว่าการทำกำไรเป็นเรื่องง่าย แต่เมื่อเริ่มต้นจริงจะพบว่ามีปัจจัยมากมายที่ต้องเรียนรู้ ทั้งเทคนิค เวทมนตร์พื้นฐาน อารมณ์ตลาด และจิตวิทยาของตน
3️⃣ ความโลภและความหวังทำให้ติดอยู่ในตลาด
• หลายคนเริ่มต้นเทรดด้วยเป้าหมายหาเหรียญทอง แต่เมื่อขาดทุน กลับพยายามเอาคืน • เมื่อกำไร ก็อยากได้มากขึ้น จนบางครั้งไม่รู้จักพอ
4️⃣ ไม่มีเส้นทางที่แน่นอน
• ในเขาวงกตนี้ ไม่มีทางเดินตรงไปสู่ความสำเร็จ ต้องลองผิดลองถูกหลายครา • บางคนหลงทาง บางคนเจอทางตัน บางคนออกจากตลาดไปก่อนจะถึงทางออกที่แท้จริง
🎯 แล้วจะเอาตัวรอดจากวงกตนี้ได้อย่างไร?
✅ เข้าใจว่าเทรดไม่ใช่การพนัน • การเทรดที่ดีต้องมีระบบ ไม่ใช่แค่เสี่ยงดวง ✅ ฝึกวินัยและจัดการอารมณ์ • สิ่งที่สังหารนักรบมิใช่ปีศาจในตลาด แต่เป็น “อารมณ์ของตนเอง” ✅ วางแผนก่อนเข้าเทรด และมีจุดตัดขาดทุนเสมอ • อย่าเข้าเทรดโดยไร้แผน เพราะจะทำให้ท่านติดอยู่ในเขาวงกตตลอดกาล ✅ รู้ว่าเมื่อไหร่ควรหยุด • บางครั้ง “การไม่เทรด” คือการตัดสินใจที่ดีที่สุด
🔮 บทสรุป
ดันเจี้ยนแห่งการเทรดเปรียบเสมือนสถานที่ลี้ลับที่ยังไม่มีผู้ใดสำรวจมาก่อน ผู้ใดที่ย่างกรายเข้ามาล้วนออกไปยาก เพราะมันเต็มไปด้วยความท้าทาย อารมณ์ และความโลภ แต่หากท่านเข้าใจเกมนี้ดีพอ ท่านจะสามารถหาทางออก และเปลี่ยนมันให้เป็นโอกาสแห่งความมั่งคั่งได้ จงจำไว้ว่า การจะออกจากดันเจี้ยนนี้ได้ ท่านต้องพิชิตบอสใหญ่ "การรู้เท่าทันอารมณ์ และมายเซ็ทที่เหมาะสมกับเทรนด์เดอร์" ให้จงได้!
หวังว่าพวกท่านจะไม่หลายเป็นซากศพเน่าๆ ในดันเจี้ยนแห่งนี้
ของให้โชคดีมีชัยในโลกเทรนด์เดอร์ YONOSUBA
-
 @ e3ba5e1a:5e433365
2025-02-05 17:47:16
@ e3ba5e1a:5e433365
2025-02-05 17:47:16I got into a friendly discussion on X regarding health insurance. The specific question was how to deal with health insurance companies (presumably unfairly) denying claims? My answer, as usual: get government out of it!
The US healthcare system is essentially the worst of both worlds:
- Unlike full single payer, individuals incur high costs
- Unlike a true free market, regulation causes increases in costs and decreases competition among insurers
I'm firmly on the side of moving towards the free market. (And I say that as someone living under a single payer system now.) Here's what I would do:
- Get rid of tax incentives that make health insurance tied to your employer, giving individuals back proper freedom of choice.
- Reduce regulations significantly.
-
In the short term, some people will still get rejected claims and other obnoxious behavior from insurance companies. We address that in two ways:
- Due to reduced regulations, new insurance companies will be able to enter the market offering more reliable coverage and better rates, and people will flock to them because they have the freedom to make their own choices.
- Sue the asses off of companies that reject claims unfairly. And ideally, as one of the few legitimate roles of government in all this, institute new laws that limit the ability of fine print to allow insurers to escape their responsibilities. (I'm hesitant that the latter will happen due to the incestuous relationship between Congress/regulators and insurers, but I can hope.)
Will this magically fix everything overnight like politicians normally promise? No. But it will allow the market to return to a healthy state. And I don't think it will take long (order of magnitude: 5-10 years) for it to come together, but that's just speculation.
And since there's a high correlation between those who believe government can fix problems by taking more control and demanding that only credentialed experts weigh in on a topic (both points I strongly disagree with BTW): I'm a trained actuary and worked in the insurance industry, and have directly seen how government regulation reduces competition, raises prices, and harms consumers.
And my final point: I don't think any prior art would be a good comparison for deregulation in the US, it's such a different market than any other country in the world for so many reasons that lessons wouldn't really translate. Nonetheless, I asked Grok for some empirical data on this, and at best the results of deregulation could be called "mixed," but likely more accurately "uncertain, confused, and subject to whatever interpretation anyone wants to apply."
https://x.com/i/grok/share/Zc8yOdrN8lS275hXJ92uwq98M
-
 @ 91bea5cd:1df4451c
2025-02-04 17:24:50
@ 91bea5cd:1df4451c
2025-02-04 17:24:50Definição de ULID:
Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível.
Gerar ULID
```sql
CREATE EXTENSION IF NOT EXISTS pgcrypto;
CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\000\000\000\000\000\000'; output TEXT = '';
unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER);
-- 10 entropy bytes ulid = timestamp || gen_random_bytes(10);
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ```
ULID TO UUID
```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF;
v = regexp_split_to_array(ulid, '');
-- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]);
-- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]);
RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE;
CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ```
UUID to ULID
```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ```
Gera 11 Digitos aleatórios: YBKXG0CKTH4
```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto;
-- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT;
-- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars;END; $$ LANGUAGE plpgsql; ```
Exemplo de USO
```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL );
-- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ```
Fontes
- https://github.com/scoville/pgsql-ulid
- https://github.com/geckoboard/pgulid
-
 @ 91bea5cd:1df4451c
2025-02-04 17:15:57
@ 91bea5cd:1df4451c
2025-02-04 17:15:57Definição de ULID:
Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível.
Gerar ULID
```sql
CREATE EXTENSION IF NOT EXISTS pgcrypto;
CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\000\000\000\000\000\000'; output TEXT = '';
unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER);
-- 10 entropy bytes ulid = timestamp || gen_random_bytes(10);
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ```
ULID TO UUID
```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF;
v = regexp_split_to_array(ulid, '');
-- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]);
-- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]);
RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE;
CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ```
UUID to ULID
```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ```
Gera 11 Digitos aleatórios: YBKXG0CKTH4
```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto;
-- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT;
-- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars;END; $$ LANGUAGE plpgsql; ```
Exemplo de USO
```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL );
-- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ```
Fontes
- https://github.com/scoville/pgsql-ulid
- https://github.com/geckoboard/pgulid
-
 @ e3ba5e1a:5e433365
2025-02-04 08:29:00
@ e3ba5e1a:5e433365
2025-02-04 08:29:00President Trump has started rolling out his tariffs, something I blogged about in November. People are talking about these tariffs a lot right now, with many people (correctly) commenting on how consumers will end up with higher prices as a result of these tariffs. While that part is true, I’ve seen a lot of people taking it to the next, incorrect step: that consumers will pay the entirety of the tax. I put up a poll on X to see what people thought, and while the right answer got a lot of votes, it wasn't the winner.

For purposes of this blog post, our ultimate question will be the following:
- Suppose apples currently sell for $1 each in the entire United States.
- There are domestic sellers and foreign sellers of apples, all receiving the same price.
- There are no taxes or tariffs on the purchase of apples.
- The question is: if the US federal government puts a $0.50 import tariff per apple, what will be the change in the following:
- Number of apples bought in the US
- Price paid by buyers for apples in the US
- Post-tax price received by domestic apple producers
- Post-tax price received by foreign apple producers
Before we can answer that question, we need to ask an easier, first question: before instituting the tariff, why do apples cost $1?
And finally, before we dive into the details, let me provide you with the answers to the ultimate question. I recommend you try to guess these answers before reading this, and if you get it wrong, try to understand why:
- The number of apples bought will go down
- The buyers will pay more for each apple they buy, but not the full amount of the tariff
- Domestic apple sellers will receive a higher price per apple
- Foreign apple sellers will receive a lower price per apple, but not lowered by the full amount of the tariff
In other words, regardless of who sends the payment to the government, both taxed parties (domestic buyers and foreign sellers) will absorb some of the costs of the tariff, while domestic sellers will benefit from the protectionism provided by tariffs and be able to sell at a higher price per unit.
Marginal benefit
All of the numbers discussed below are part of a helper Google Sheet I put together for this analysis. Also, apologies about the jagged lines in the charts below, I hadn’t realized before starting on this that there are some difficulties with creating supply and demand charts in Google Sheets.
Let’s say I absolutely love apples, they’re my favorite food. How much would I be willing to pay for a single apple? You might say “$1, that’s the price in the supermarket,” and in many ways you’d be right. If I walk into supermarket A, see apples on sale for $50, and know that I can buy them at supermarket B for $1, I’ll almost certainly leave A and go buy at B.
But that’s not what I mean. What I mean is: how high would the price of apples have to go everywhere so that I’d no longer be willing to buy a single apple? This is a purely personal, subjective opinion. It’s impacted by how much money I have available, other expenses I need to cover, and how much I like apples. But let’s say the number is $5.
How much would I be willing to pay for another apple? Maybe another $5. But how much am I willing to pay for the 1,000th apple? 10,000th? At some point, I’ll get sick of apples, or run out of space to keep the apples, or not be able to eat, cook, and otherwise preserve all those apples before they rot.
The point being: I’ll be progressively willing to spend less and less money for each apple. This form of analysis is called marginal benefit: how much benefit (expressed as dollars I’m willing to spend) will I receive from each apple? This is a downward sloping function: for each additional apple I buy (quantity demanded), the price I’m willing to pay goes down. This is what gives my personal demand curve. And if we aggregate demand curves across all market participants (meaning: everyone interested in buying apples), we end up with something like this:
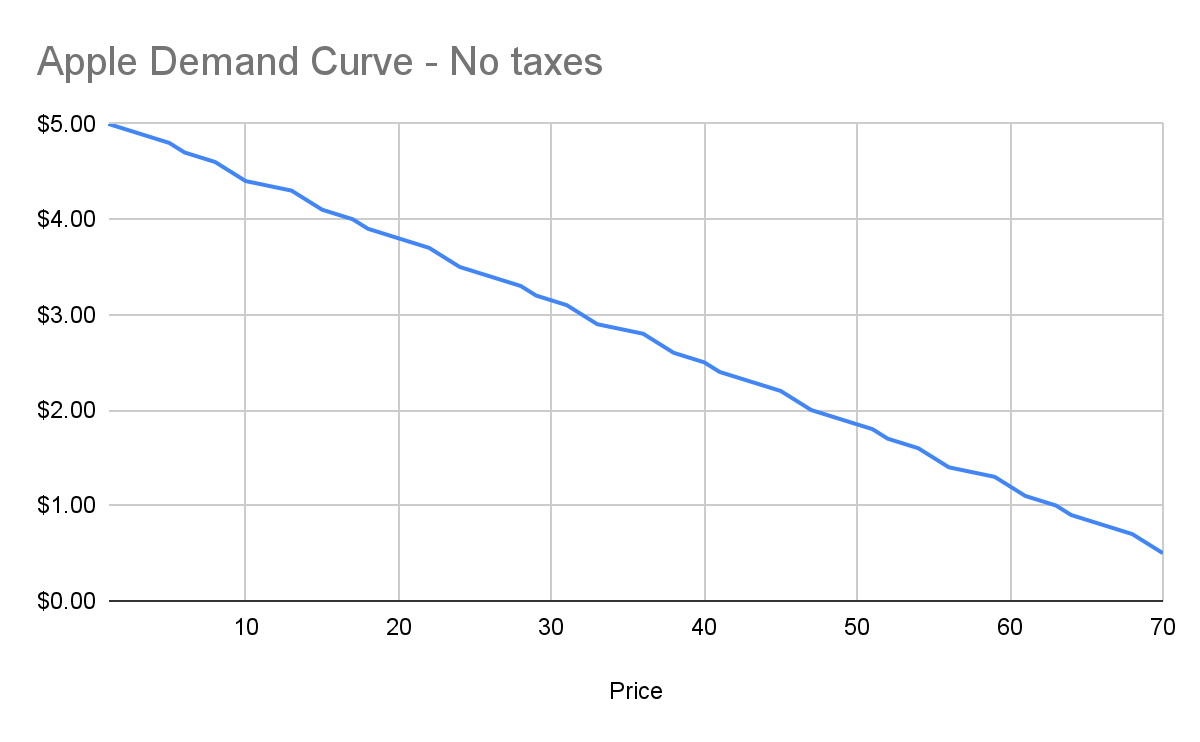
Assuming no changes in people’s behavior and other conditions in the market, this chart tells us how many apples will be purchased by our buyers at each price point between $0.50 and $5. And ceteris paribus (all else being equal), this will continue to be the demand curve for apples.
Marginal cost
Demand is half the story of economics. The other half is supply, or: how many apples will I sell at each price point? Supply curves are upward sloping: the higher the price, the more a person or company is willing and able to sell a product.
Let’s understand why. Suppose I have an apple orchard. It’s a large property right next to my house. With about 2 minutes of effort, I can walk out of my house, find the nearest tree, pick 5 apples off the tree, and call it a day. 5 apples for 2 minutes of effort is pretty good, right?
Yes, there was all the effort necessary to buy the land, and plant the trees, and water them… and a bunch more than I likely can’t even guess at. We’re going to ignore all of that for our analysis, because for short-term supply-and-demand movement, we can ignore these kinds of sunk costs. One other simplification: in reality, supply curves often start descending before ascending. This accounts for achieving efficiencies of scale after the first number of units purchased. But since both these topics are unneeded for understanding taxes, I won’t go any further.
Anyway, back to my apple orchard. If someone offers me $0.50 per apple, I can do 2 minutes of effort and get $2.50 in revenue, which equates to a $75/hour wage for me. I’m more than happy to pick apples at that price!
However, let’s say someone comes to buy 10,000 apples from me instead. I no longer just walk out to my nearest tree. I’m going to need to get in my truck, drive around, spend the day in the sun, pay for gas, take a day off of my day job (let’s say it pays me $70/hour). The costs go up significantly. Let’s say it takes 5 days to harvest all those apples myself, it costs me $100 in fuel and other expenses, and I lose out on my $70/hour job for 5 days. We end up with:
- Total expenditure: $100 + $70 * 8 hours a day * 5 days \== $2900
- Total revenue: $5000 (10,000 apples at $0.50 each)
- Total profit: $2100
So I’m still willing to sell the apples at this price, but it’s not as attractive as before. And as the number of apples purchased goes up, my costs keep increasing. I’ll need to spend more money on fuel to travel more of my property. At some point I won’t be able to do the work myself anymore, so I’ll need to pay others to work on the farm, and they’ll be slower at picking apples than me (less familiar with the property, less direct motivation, etc.). The point being: at some point, the number of apples can go high enough that the $0.50 price point no longer makes me any money.
This kind of analysis is called marginal cost. It refers to the additional amount of expenditure a seller has to spend in order to produce each additional unit of the good. Marginal costs go up as quantity sold goes up. And like demand curves, if you aggregate this data across all sellers, you get a supply curve like this:
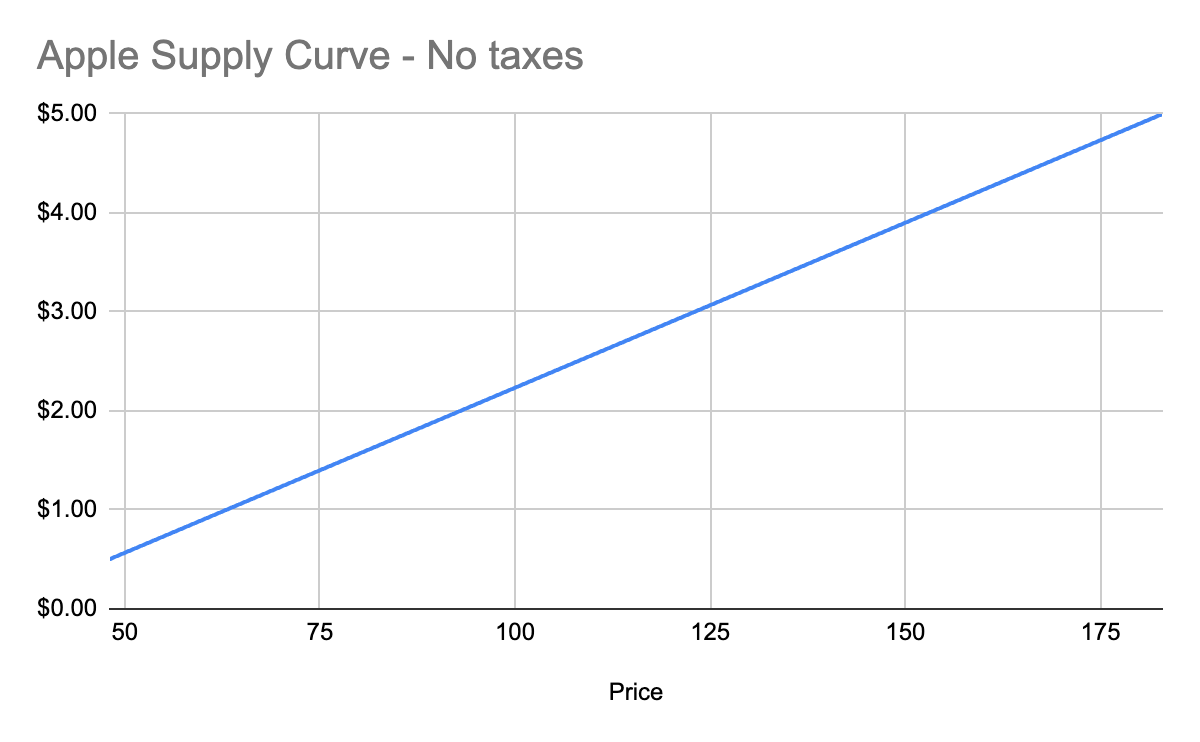
Equilibrium price
We now know, for every price point, how many apples buyers will purchase, and how many apples sellers will sell. Now we find the equilibrium: where the supply and demand curves meet. This point represents where the marginal benefit a buyer would receive from the next buyer would be less than the cost it would take the next seller to make it. Let’s see it in a chart:
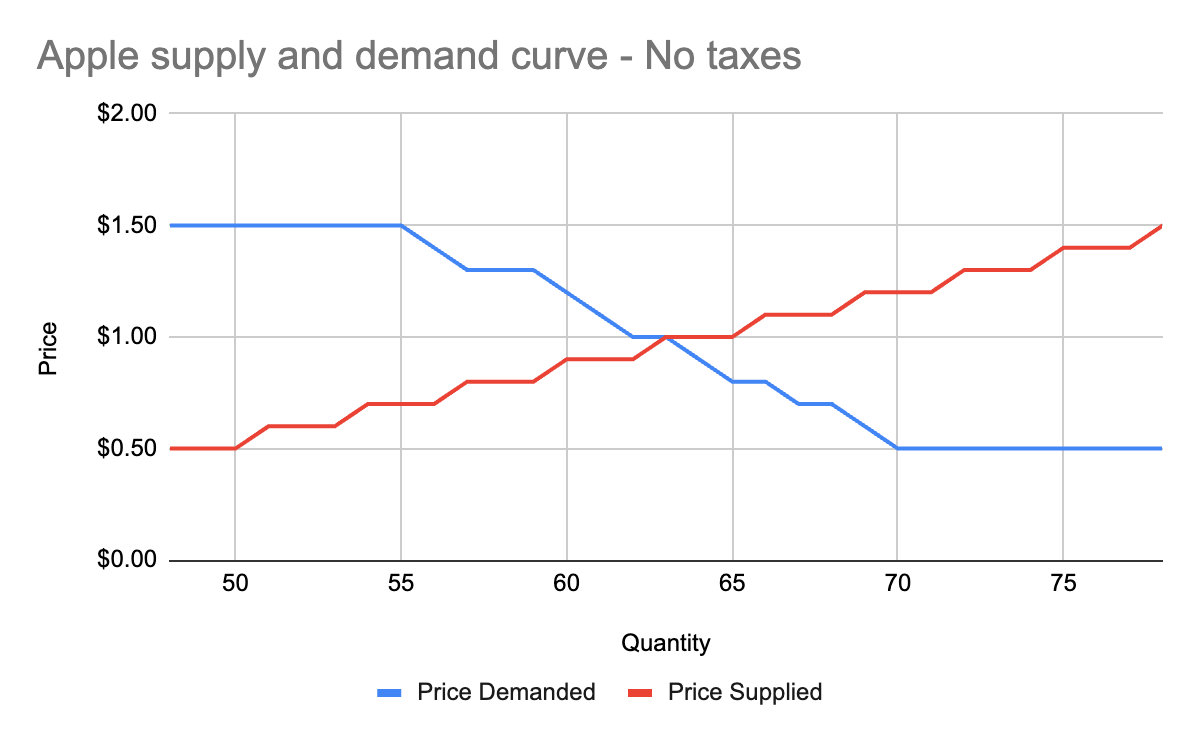
You’ll notice that these two graphs cross at the $1 price point, where 63 apples are both demanded (bought by consumers) and supplied (sold by producers). This is our equilibrium price. We also have a visualization of the surplus created by these trades. Everything to the left of the equilibrium point and between the supply and demand curves represents surplus: an area where someone is receiving something of more value than they give. For example:
- When I bought my first apple for $1, but I was willing to spend $5, I made $4 of consumer surplus. The consumer portion of the surplus is everything to the left of the equilibrium point, between the supply and demand curves, and above the equilibrium price point.
- When a seller sells his first apple for $1, but it only cost $0.50 to produce it, the seller made $0.50 of producer surplus. The producer portion of the surplus is everything to the left of the equilibrium point, between the supply and demand curves, and below the equilibrium price point.
Another way of thinking of surplus is “every time someone got a better price than they would have been willing to take.”
OK, with this in place, we now have enough information to figure out how to price in the tariff, which we’ll treat as a negative externality.
Modeling taxes
Alright, the government has now instituted a $0.50 tariff on every apple sold within the US by a foreign producer. We can generally model taxes by either increasing the marginal cost of each unit sold (shifting the supply curve up), or by decreasing the marginal benefit of each unit bought (shifting the demand curve down). In this case, since only some of the producers will pay the tax, it makes more sense to modify the supply curve.
First, let’s see what happens to the foreign seller-only supply curve when you add in the tariff:
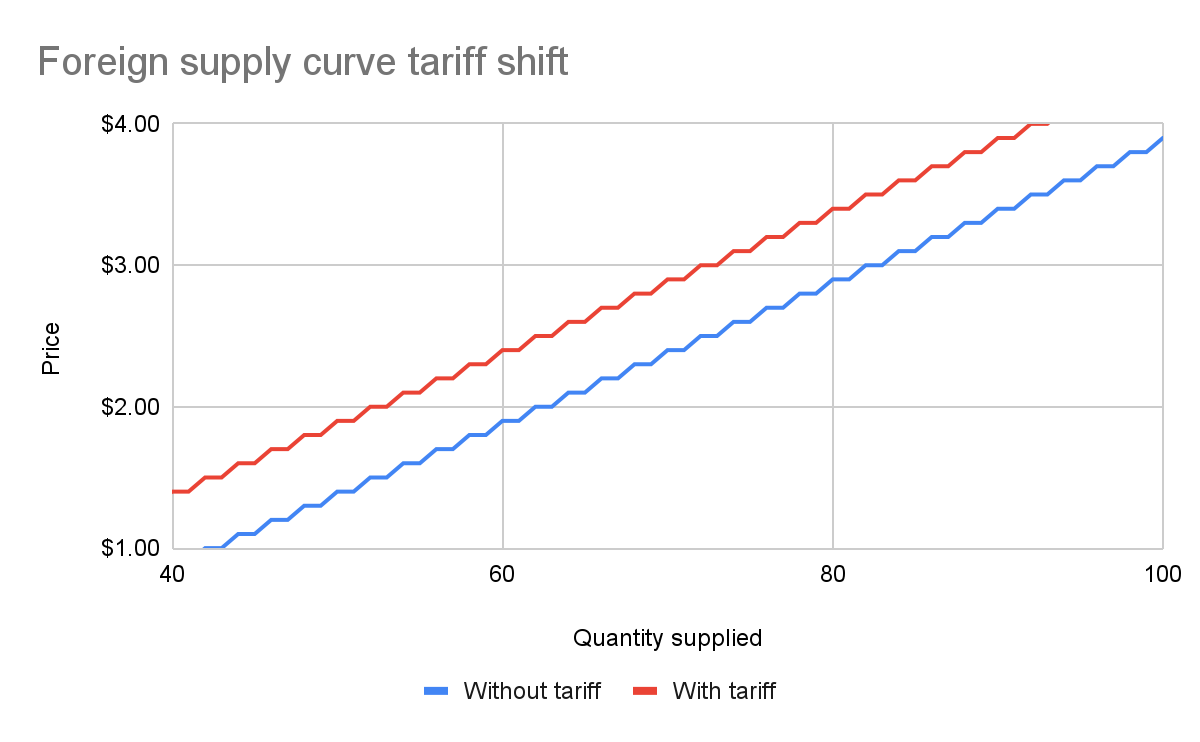
With the tariff in place, for each quantity level, the price at which the seller will sell is $0.50 higher than before the tariff. That makes sense: if I was previously willing to sell my 82nd apple for $3, I would now need to charge $3.50 for that apple to cover the cost of the tariff. We see this as the tariff “pushing up” or “pushing left” the original supply curve.
We can add this new supply curve to our existing (unchanged) supply curve for domestic-only sellers, and we end up with a result like this:
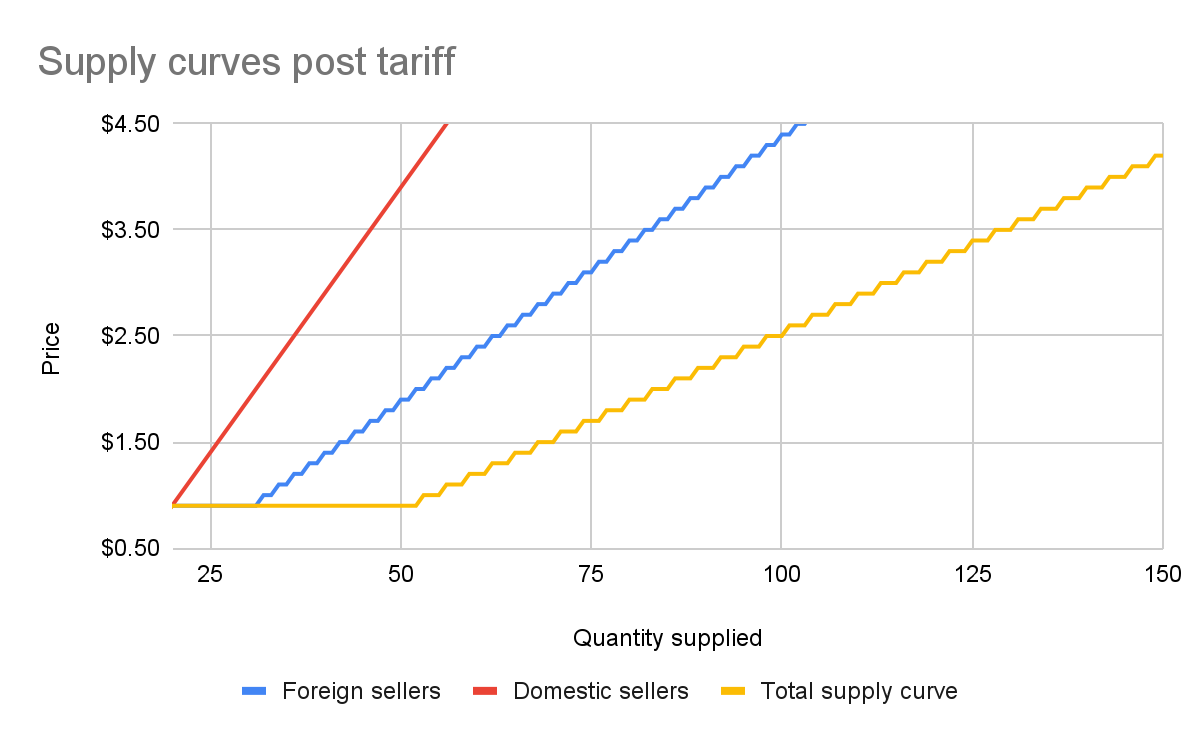
The total supply curve adds up the individual foreign and domestic supply curves. At each price point, we add up the total quantity each group would be willing to sell to determine the total quantity supplied for each price point. Once we have that cumulative supply curve defined, we can produce an updated supply-and-demand chart including the tariff:
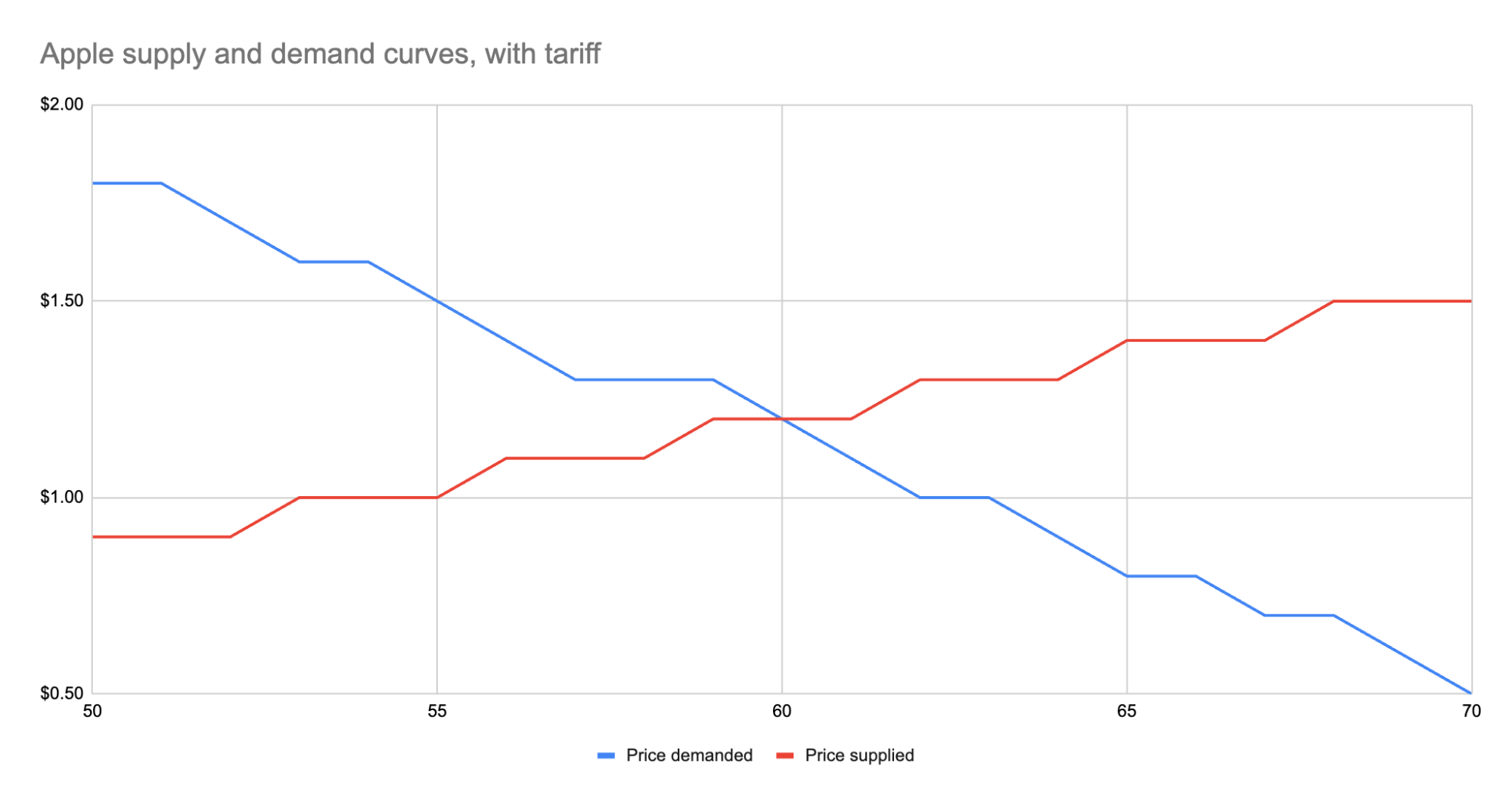
As we can see, the equilibrium has shifted:
- The equilibrium price paid by consumers has risen from $1 to $1.20.
- The total number of apples purchased has dropped from 63 apples to 60 apples.
- Consumers therefore received 3 less apples. They spent $72 for these 60 apples, whereas previously they spent $63 for 3 more apples, a definite decrease in consumer surplus.
- Foreign producers sold 36 of those apples (see the raw data in the linked Google Sheet), for a gross revenue of $43.20. However, they also need to pay the tariff to the US government, which accounts for $18, meaning they only receive $25.20 post-tariff. Previously, they sold 42 apples at $1 each with no tariff to be paid, meaning they took home $42.
- Domestic producers sold the remaining 24 apples at $1.20, giving them a revenue of $28.80. Since they don’t pay the tariff, they take home all of that money. By contrast, previously, they sold 21 apples at $1, for a take-home of $21.
- The government receives $0.50 for each of the 60 apples sold, or in other words receives $30 in revenue it wouldn’t have received otherwise.
We could be more specific about the surpluses, and calculate the actual areas for consumer surplus, producer surplus, inefficiency from the tariff, and government revenue from the tariff. But I won’t bother, as those calculations get slightly more involved. Instead, let’s just look at the aggregate outcomes:
- Consumers were unquestionably hurt. Their price paid went up by $0.20 per apple, and received less apples.
- Foreign producers were also hurt. Their price received went down from the original $1 to the new post-tariff price of $1.20, minus the $0.50 tariff. In other words: foreign producers only receive $0.70 per apple now. This hurt can be mitigated by shifting sales to other countries without a tariff, but the pain will exist regardless.
- Domestic producers scored. They can sell less apples and make more revenue doing it.
- And the government walked away with an extra $30.
Hopefully you now see the answer to the original questions. Importantly, while the government imposed a $0.50 tariff, neither side fully absorbed that cost. Consumers paid a bit more, foreign producers received a bit less. The exact details of how that tariff was split across the groups is mediated by the relevant supply and demand curves of each group. If you want to learn more about this, the relevant search term is “price elasticity,” or how much a group’s quantity supplied or demanded will change based on changes in the price.
Other taxes
Most taxes are some kind of a tax on trade. Tariffs on apples is an obvious one. But the same applies to income tax (taxing the worker for the trade of labor for money) or payroll tax (same thing, just taxing the employer instead). Interestingly, you can use the same model for analyzing things like tax incentives. For example, if the government decided to subsidize domestic apple production by giving the domestic producers a $0.50 bonus for each apple they sell, we would end up with a similar kind of analysis, except instead of the foreign supply curve shifting up, we’d see the domestic supply curve shifting down.
And generally speaking, this is what you’ll always see with government involvement in the economy. It will result in disrupting an existing equilibrium, letting the market readjust to a new equilibrium, and incentivization of some behavior, causing some people to benefit and others to lose out. We saw with the apple tariff, domestic producers and the government benefited while others lost.
You can see the reverse though with tax incentives. If I give a tax incentive of providing a deduction (not paying income tax) for preschool, we would end up with:
- Government needs to make up the difference in tax revenue, either by raising taxes on others or printing more money (leading to inflation). Either way, those paying the tax or those holding government debased currency will pay a price.
- Those people who don’t use the preschool deduction will receive no benefit, so they simply pay a cost.
- Those who do use the preschool deduction will end up paying less on tax+preschool than they would have otherwise.
This analysis is fully amoral. It’s not saying whether providing subsidized preschool is a good thing or not, it simply tells you where the costs will be felt, and points out that such government interference in free economic choice does result in inefficiencies in the system. Once you have that knowledge, you’re more well educated on making a decision about whether the costs of government intervention are worth the benefits.
-
 @ 9e69e420:d12360c2
2025-02-01 11:16:04
@ 9e69e420:d12360c2
2025-02-01 11:16:04Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.

CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language.
One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse.
-
 @ 97c70a44:ad98e322
2025-01-30 17:15:37
@ 97c70a44:ad98e322
2025-01-30 17:15:37There was a slight dust up recently over a website someone runs removing a listing for an app someone built based on entirely arbitrary criteria. I'm not to going to attempt to speak for either wounded party, but I would like to share my own personal definition for what constitutes a "nostr app" in an effort to help clarify what might be an otherwise confusing and opaque purity test.
In this post, I will be committing the "no true Scotsman" fallacy, in which I start with the most liberal definition I can come up with, and gradually refine it until all that is left is the purest, gleamingest, most imaginary and unattainable nostr app imaginable. As I write this, I wonder if anything built yet will actually qualify. In any case, here we go.
It uses nostr
The lowest bar for what a "nostr app" might be is an app ("application" - i.e. software, not necessarily a native app of any kind) that has some nostr-specific code in it, but which doesn't take any advantage of what makes nostr distinctive as a protocol.
Examples might include a scraper of some kind which fulfills its charter by fetching data from relays (regardless of whether it validates or retains signatures). Another might be a regular web 2.0 app which provides an option to "log in with nostr" by requesting and storing the user's public key.
In either case, the fact that nostr is involved is entirely neutral. A scraper can scrape html, pdfs, jsonl, whatever data source - nostr relays are just another target. Likewise, a user's key in this scenario is treated merely as an opaque identifier, with no appreciation for the super powers it brings along.
In most cases, this kind of app only exists as a marketing ploy, or less cynically, because it wants to get in on the hype of being a "nostr app", without the developer quite understanding what that means, or having the budget to execute properly on the claim.
It leverages nostr
Some of you might be wondering, "isn't 'leverage' a synonym for 'use'?" And you would be right, but for one connotative difference. It's possible to "use" something improperly, but by definition leverage gives you a mechanical advantage that you wouldn't otherwise have. This is the second category of "nostr app".
This kind of app gets some benefit out of the nostr protocol and network, but in an entirely selfish fashion. The intention of this kind of app is not to augment the nostr network, but to augment its own UX by borrowing some nifty thing from the protocol without really contributing anything back.
Some examples might include:
- Using nostr signers to encrypt or sign data, and then store that data on a proprietary server.
- Using nostr relays as a kind of low-code backend, but using proprietary event payloads.
- Using nostr event kinds to represent data (why), but not leveraging the trustlessness that buys you.
An application in this category might even communicate to its users via nostr DMs - but this doesn't make it a "nostr app" any more than a website that emails you hot deals on herbal supplements is an "email app". These apps are purely parasitic on the nostr ecosystem.
In the long-term, that's not necessarily a bad thing. Email's ubiquity is self-reinforcing. But in the short term, this kind of "nostr app" can actually do damage to nostr's reputation by over-promising and under-delivering.
It complements nostr
Next up, we have apps that get some benefit out of nostr as above, but give back by providing a unique value proposition to nostr users as nostr users. This is a bit of a fine distinction, but for me this category is for apps which focus on solving problems that nostr isn't good at solving, leaving the nostr integration in a secondary or supporting role.
One example of this kind of app was Mutiny (RIP), which not only allowed users to sign in with nostr, but also pulled those users' social graphs so that users could send money to people they knew and trusted. Mutiny was doing a great job of leveraging nostr, as well as providing value to users with nostr identities - but it was still primarily a bitcoin wallet, not a "nostr app" in the purest sense.
Other examples are things like Nostr Nests and Zap.stream, whose core value proposition is streaming video or audio content. Both make great use of nostr identities, data formats, and relays, but they're primarily streaming apps. A good litmus test for things like this is: if you got rid of nostr, would it be the same product (even if inferior in certain ways)?
A similar category is infrastructure providers that benefit nostr by their existence (and may in fact be targeted explicitly at nostr users), but do things in a centralized, old-web way; for example: media hosts, DNS registrars, hosting providers, and CDNs.
To be clear here, I'm not casting aspersions (I don't even know what those are, or where to buy them). All the apps mentioned above use nostr to great effect, and are a real benefit to nostr users. But they are not True Scotsmen.
It embodies nostr
Ok, here we go. This is the crème de la crème, the top du top, the meilleur du meilleur, the bee's knees. The purest, holiest, most chaste category of nostr app out there. The apps which are, indeed, nostr indigitate.
This category of nostr app (see, no quotes this time) can be defined by the converse of the previous category. If nostr was removed from this type of application, would it be impossible to create the same product?
To tease this apart a bit, apps that leverage the technical aspects of nostr are dependent on nostr the protocol, while apps that benefit nostr exclusively via network effect are integrated into nostr the network. An app that does both things is working in symbiosis with nostr as a whole.
An app that embraces both nostr's protocol and its network becomes an organic extension of every other nostr app out there, multiplying both its competitive moat and its contribution to the ecosystem:
- In contrast to apps that only borrow from nostr on the technical level but continue to operate in their own silos, an application integrated into the nostr network comes pre-packaged with existing users, and is able to provide more value to those users because of other nostr products. On nostr, it's a good thing to advertise your competitors.
- In contrast to apps that only market themselves to nostr users without building out a deep integration on the protocol level, a deeply integrated app becomes an asset to every other nostr app by becoming an organic extension of them through interoperability. This results in increased traffic to the app as other developers and users refer people to it instead of solving their problem on their own. This is the "micro-apps" utopia we've all been waiting for.
Credible exit doesn't matter if there aren't alternative services. Interoperability is pointless if other applications don't offer something your app doesn't. Marketing to nostr users doesn't matter if you don't augment their agency as nostr users.
If I had to choose a single NIP that represents the mindset behind this kind of app, it would be NIP 89 A.K.A. "Recommended Application Handlers", which states:
Nostr's discoverability and transparent event interaction is one of its most interesting/novel mechanics. This NIP provides a simple way for clients to discover applications that handle events of a specific kind to ensure smooth cross-client and cross-kind interactions.
These handlers are the glue that holds nostr apps together. A single event, signed by the developer of an application (or by the application's own account) tells anyone who wants to know 1. what event kinds the app supports, 2. how to link to the app (if it's a client), and (if the pubkey also publishes a kind 10002), 3. which relays the app prefers.
As a sidenote, NIP 89 is currently focused more on clients, leaving DVMs, relays, signers, etc somewhat out in the cold. Updating 89 to include tailored listings for each kind of supporting app would be a huge improvement to the protocol. This, plus a good front end for navigating these listings (sorry nostrapp.link, close but no cigar) would obviate the evil centralized websites that curate apps based on arbitrary criteria.
Examples of this kind of app obviously include many kind 1 clients, as well as clients that attempt to bring the benefits of the nostr protocol and network to new use cases - whether long form content, video, image posts, music, emojis, recipes, project management, or any other "content type".
To drill down into one example, let's think for a moment about forms. What's so great about a forms app that is built on nostr? Well,
- There is a spec for forms and responses, which means that...
- Multiple clients can implement the same data format, allowing for credible exit and user choice, even of...
- Other products not focused on forms, which can still view, respond to, or embed forms, and which can send their users via NIP 89 to a client that does...
- Cryptographically sign forms and responses, which means they are self-authenticating and can be sent to...
- Multiple relays, which reduces the amount of trust necessary to be confident results haven't been deliberately "lost".
Show me a forms product that does all of those things, and isn't built on nostr. You can't, because it doesn't exist. Meanwhile, there are plenty of image hosts with APIs, streaming services, and bitcoin wallets which have basically the same levels of censorship resistance, interoperability, and network effect as if they weren't built on nostr.
It supports nostr
Notice I haven't said anything about whether relays, signers, blossom servers, software libraries, DVMs, and the accumulated addenda of the nostr ecosystem are nostr apps. Well, they are (usually).
This is the category of nostr app that gets none of the credit for doing all of the work. There's no question that they qualify as beautiful nostrcorns, because their value propositions are entirely meaningless outside of the context of nostr. Who needs a signer if you don't have a cryptographic identity you need to protect? DVMs are literally impossible to use without relays. How are you going to find the blossom server that will serve a given hash if you don't know which servers the publishing user has selected to store their content?
In addition to being entirely contextualized by nostr architecture, this type of nostr app is valuable because it does things "the nostr way". By that I mean that they don't simply try to replicate existing internet functionality into a nostr context; instead, they create entirely new ways of putting the basic building blocks of the internet back together.
A great example of this is how Nostr Connect, Nostr Wallet Connect, and DVMs all use relays as brokers, which allows service providers to avoid having to accept incoming network connections. This opens up really interesting possibilities all on its own.
So while I might hesitate to call many of these things "apps", they are certainly "nostr".
Appendix: it smells like a NINO
So, let's say you've created an app, but when you show it to people they politely smile, nod, and call it a NINO (Nostr In Name Only). What's a hacker to do? Well, here's your handy-dandy guide on how to wash that NINO stench off and Become a Nostr.
You app might be a NINO if:
- There's no NIP for your data format (or you're abusing NIP 78, 32, etc by inventing a sub-protocol inside an existing event kind)
- There's a NIP, but no one knows about it because it's in a text file on your hard drive (or buried in your project's repository)
- Your NIP imposes an incompatible/centralized/legacy web paradigm onto nostr
- Your NIP relies on trusted third (or first) parties
- There's only one implementation of your NIP (yours)
- Your core value proposition doesn't depend on relays, events, or nostr identities
- One or more relay urls are hard-coded into the source code
- Your app depends on a specific relay implementation to work (ahem, relay29)
- You don't validate event signatures
- You don't publish events to relays you don't control
- You don't read events from relays you don't control
- You use legacy web services to solve problems, rather than nostr-native solutions
- You use nostr-native solutions, but you've hardcoded their pubkeys or URLs into your app
- You don't use NIP 89 to discover clients and services
- You haven't published a NIP 89 listing for your app
- You don't leverage your users' web of trust for filtering out spam
- You don't respect your users' mute lists
- You try to "own" your users' data
Now let me just re-iterate - it's ok to be a NINO. We need NINOs, because nostr can't (and shouldn't) tackle every problem. You just need to decide whether your app, as a NINO, is actually contributing to the nostr ecosystem, or whether you're just using buzzwords to whitewash a legacy web software product.
If you're in the former camp, great! If you're in the latter, what are you waiting for? Only you can fix your NINO problem. And there are lots of ways to do this, depending on your own unique situation:
- Drop nostr support if it's not doing anyone any good. If you want to build a normal company and make some money, that's perfectly fine.
- Build out your nostr integration - start taking advantage of webs of trust, self-authenticating data, event handlers, etc.
- Work around the problem. Think you need a special relay feature for your app to work? Guess again. Consider encryption, AUTH, DVMs, or better data formats.
- Think your idea is a good one? Talk to other devs or open a PR to the nips repo. No one can adopt your NIP if they don't know about it.
- Keep going. It can sometimes be hard to distinguish a research project from a NINO. New ideas have to be built out before they can be fully appreciated.
- Listen to advice. Nostr developers are friendly and happy to help. If you're not sure why you're getting traction, ask!
I sincerely hope this article is useful for all of you out there in NINO land. Maybe this made you feel better about not passing the totally optional nostr app purity test. Or maybe it gave you some actionable next steps towards making a great NINON (Nostr In Not Only Name) app. In either case, GM and PV.
-
 @ 9e69e420:d12360c2
2025-01-30 12:23:04
@ 9e69e420:d12360c2
2025-01-30 12:23:04Tech stocks have taken a hit globally after China's DeepSeek launched a competitive AI chatbot at a much lower cost than US counterparts. This has stirred market fears of a $1.2 trillion loss across tech companies when trading opens in New York.
DeepSeek’s chatbot quickly topped download charts and surprised experts with its capabilities, developed for only $5.6 million.
The Nasdaq dropped over 3% in premarket trading, with major firms like Nvidia falling more than 10%. SoftBank also saw losses shortly after investing in a significant US AI venture.
Venture capitalist Marc Andreessen called it “AI’s Sputnik moment,” highlighting its potential impact on the industry.
![] (https://www.telegraph.co.uk/content/dam/business/2025/01/27/TELEMMGLPICT000409807198_17379939060750_trans_NvBQzQNjv4BqgsaO8O78rhmZrDxTlQBjdGLvJF5WfpqnBZShRL_tOZw.jpeg)
