-
 @ 6d8e2a24:5faaca4c
2025-06-06 04:26:58
@ 6d8e2a24:5faaca4c
2025-06-06 04:26:58
President Donald Trump attends a meeting with the Fraternal Order of Police in the State Dinning Room of the White House, Thursday, June 5, 2025, in Washington. (AP Photo/Alex Brandon)
Last Friday, President Donald Trump heaped praise on Elon Musk as the tech billionaire prepared to leave his unorthodox White House job.
Less than a week later, their potent political alliance met a dramatic end Thursday when the men attacked each other with blistering epithets. Trump threatened to go after Musk’s business interests. Musk called for Trump’s impeachment.
social media posts urging lawmakers to oppose deficit spending and increasing the debt ceiling.
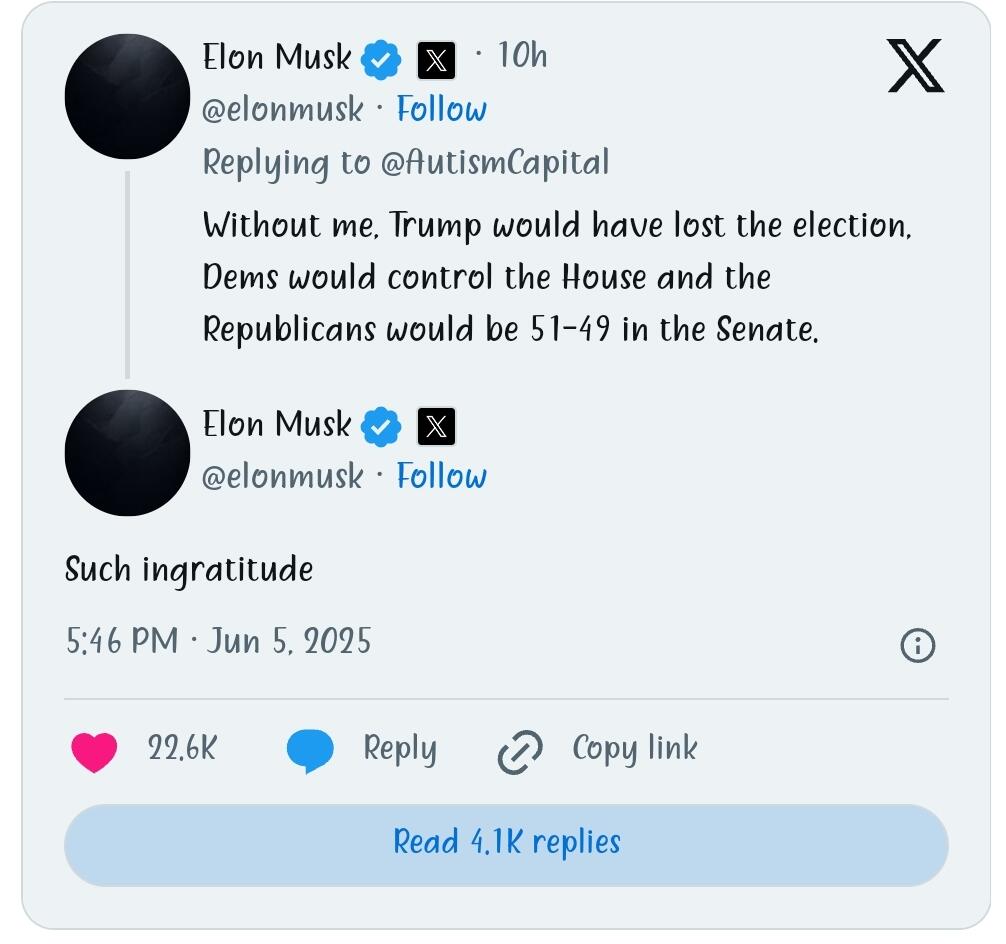
“Without me, Trump would have lost the election, Dems would control the House and the Republicans would be 51-49 in the Senate,” Musk posted, a reference to Musk’s record political spending last year, which topped $250 million.
“Such ingratitude,” he added.
Trump said Musk had worn out his welcome at the White House and was mad that Trump was changing electric vehicle policies in ways that would financially harm Musk-led Tesla.
“Elon was ‘wearing thin,’ I asked him to leave, I took away his EV Mandate that forced everyone to buy Electric Cars that nobody else wanted (that he knew for months I was going to do!), and he just went CRAZY!” Trump wrote.

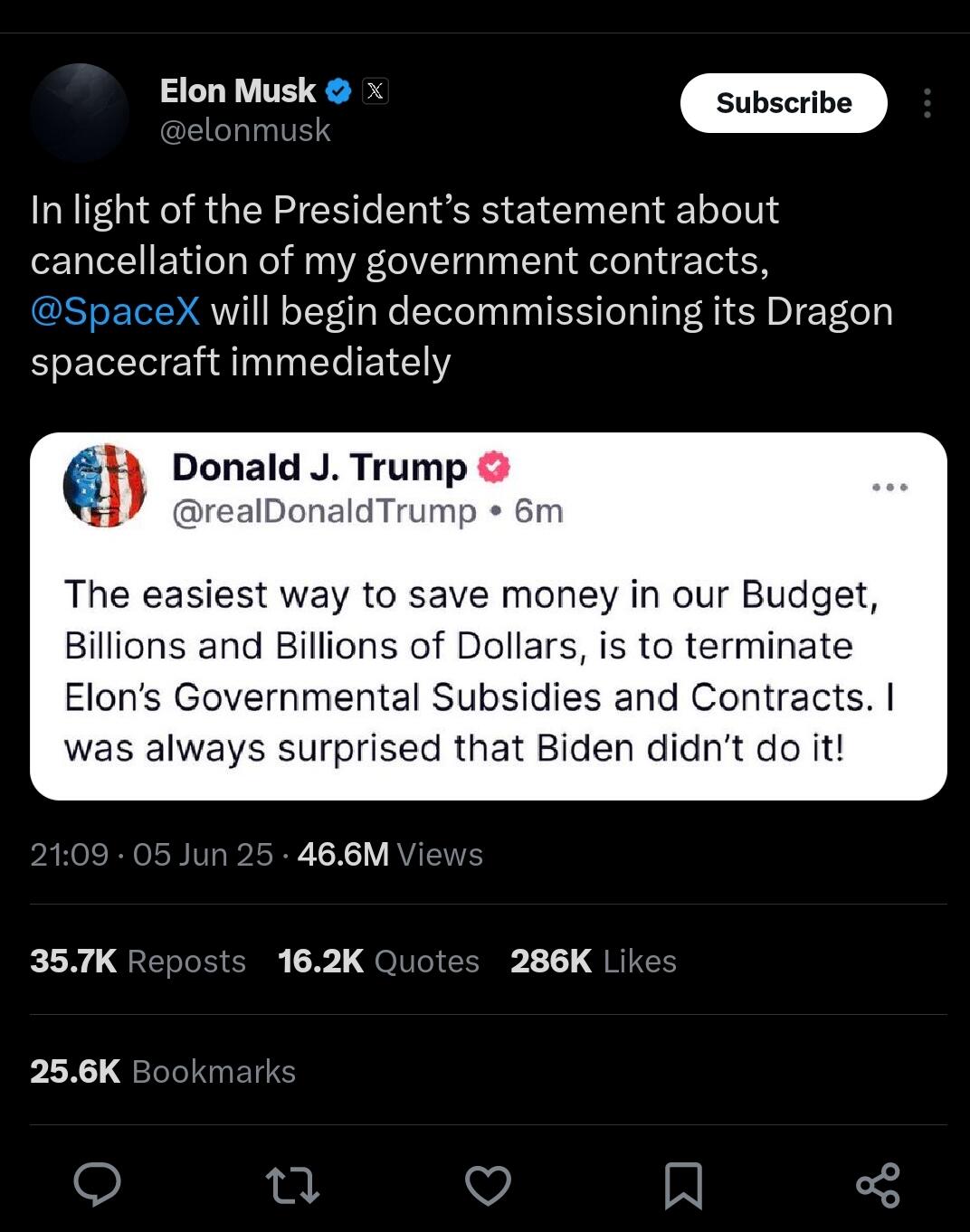
Musk goes nuclear “Time to drop the really big bomb: Trump is in the Epstein files. That is the real reason they have not been made public. Have a nice day, DJT!” — Musk, Thursday, X post.

In a series of posts, he shined a spotlight on ties between Trump and Jeffrey Epstein, the financier who killed himself while awaiting trial on federal sex trafficking charges. Some loud voices in Trump’s “Make America Great Again” movement claim Epstein’s suicide was staged by powerful figures, including prominent Democrats, who feared Epstein would expose their involvement in trafficking. Trump’s own FBI leaders have dismissed such speculation and there’s no evidence supporting it.
Later, when an X user suggested Trump be impeached and replaced by Vice President JD Vance, Musk agreed.
“Yes,” he wrote.

“I don’t mind Elon turning against me, but he should have done so months ago,” Trump wrote. He went on to promote his budget bill.
https://www.google.com/amp/s/www.wavy.com/news/politics/ap-the-implosion-of-a-powerful-political-alliance-trump-and-musk-in-their-own-words/amp/
-
 @ 6d8e2a24:5faaca4c
2025-06-06 03:09:51
@ 6d8e2a24:5faaca4c
2025-06-06 03:09:51by Claire Mom June 5, 2025 6:54 pm

*Elon Musk, the tech mogul, says US President Donald Trump would have lost the 2024 election without him.*
Musk made the comment on X in response to Trump’s criticism against him.
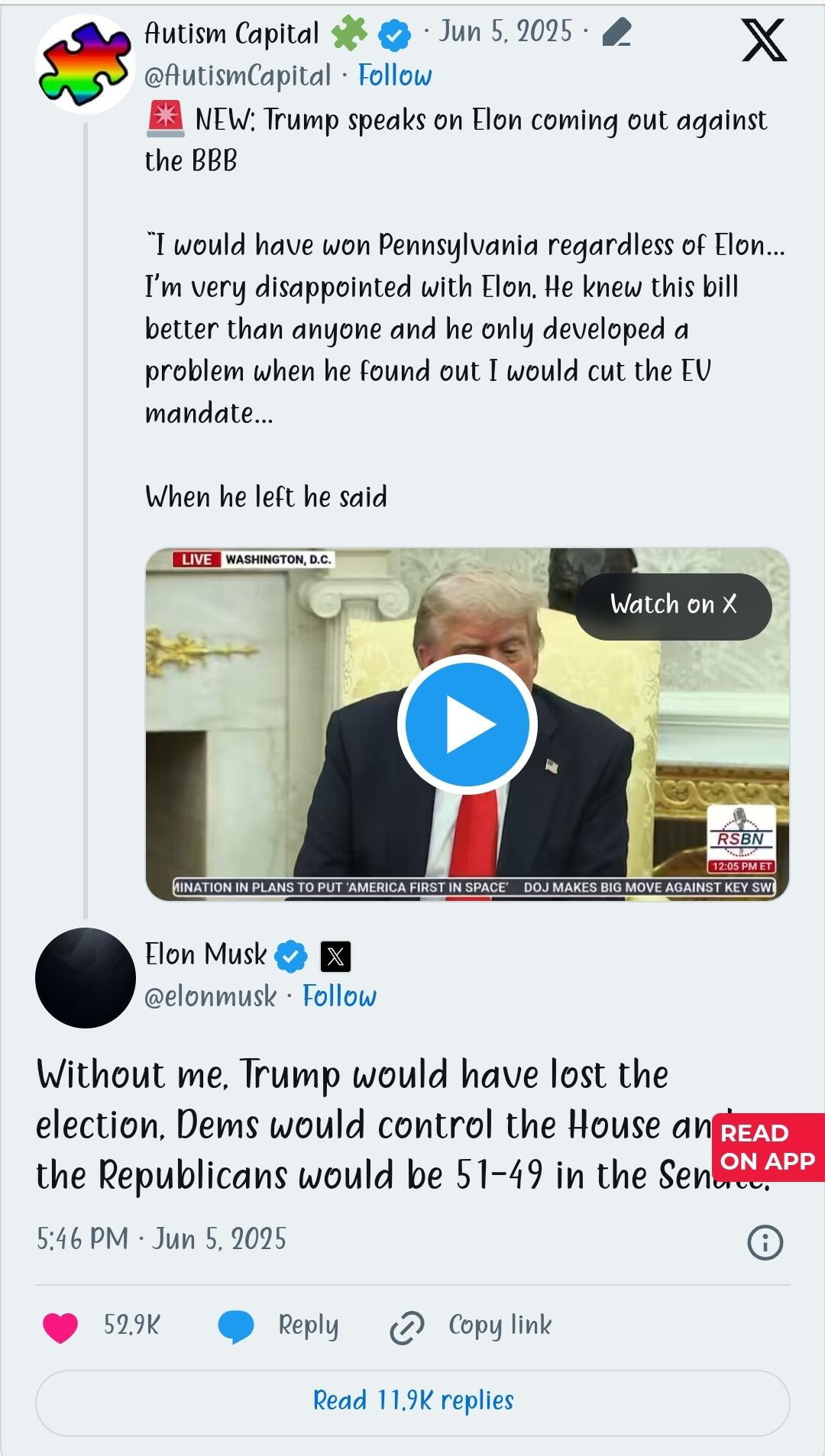
Musk, who led the department of government efficiency (DOGE), quit his role a day after he spoke out against a Trump-backed spending bill. The president called it a “Big Beautiful Bill”.
The controversial bill is a centrepiece of Trump’s second-term domestic agenda, combining major tax cuts, stricter immigration enforcement, welfare programme overhauls, and significant increases in border security funding.
The legislation sparked intense debate across the country and in Congress and was only passed after a nail-biting 215-214 vote.
The plan revived the US-Mexico border wall with a $46.5 billion budget, $350 billion for deportation efforts and border security, and a hiring spree of 10,000 new ICE agents, 5,000 customs officers, and 3,000 border patrol agents.
For the first time, migrants will be charged a $1,000 fee to apply for asylum.
The bill also authorises a $4 trillion increase to the national debt ceiling, while the estate tax exemption jumped to $15 million, benefiting wealthier Americans.
Critics including Musk called the bill fiscally irresponsible and “a disgusting abomination” due to its combination of large tax cuts and spending increases.
Musk had clamoured for DOGE’s creation to save taxpayers $2 trillion. Only $160 billion has been saved so far.
*TRUMP: I’M VERY DISAPPOINTED WITH ELON*
Since Musk’s exit from the White House last week, his criticism of the bill has grown louder.
Speaking on the issue, Trump said he was “very disappointed with Elon”.
The US president said the Tesla CEO was satisfied with the bill but only grew discontent after he found out electric vehicles would be impacted.
“I’m very disappointed because Elon knew the inner workings of this bill better than almost anybody sitting here. He knew everything about it, and all of a sudden he had a problem, and he only developed a problem when he found out I was going to cut the EV mandate because that’s billions and billions of dollars,” the president said
“And it really is unfair; we want to have cars of all types.
“He said the most beautiful things about me, and he hasn’t said anything bad about me personally, but I’m sure that will be next. But I’m really disappointed with Elon. I’ve helped Elon a lot.”
Trump praised Musk for his work at DOGE but blamed his tantrums on missing the office.
“Elon worked hard at DOGE, and I think he misses the place. I think he got out there, and all of a sudden, he’s no longer in this beautiful Oval Office,” he said.
“He’s not the first. People leave my administration, and they love us, and then at some point they miss it so badly, and some of them embrace it, and some of them actually become hostile. I don’t know what it is, some sort of Trump derangement syndrome.”
The president also said he would have won Pennsylvania, a key state, without Musk’s help.
In reaction, the billionaire businessman countered Trump.
“Without me, Trump would have lost the election, Dems would control the House, and the Republicans would be 51-49 in the Senate,” Musk tweeted.
“Such ingratitude.”
The exchange marks yet another dent in the tumultuous relationship between the two-time American president and the world’s richest man.
https://www.thecable.ng/trump-would-have-lost-election-without-me-says-elon-musk/
-
 @ 5d4b6c8d:8a1c1ee3
2025-06-06 03:04:19
@ 5d4b6c8d:8a1c1ee3
2025-06-06 03:04:19Alright stackers, how'd you do today?
What goals did you hit? What do you need to work on tomorrow?
I had another solid day, but I want to get more stretching in tomorrow.
https://stacker.news/items/998508
-
 @ 4fa51c35:55d6763d
2025-06-06 02:35:44
@ 4fa51c35:55d6763d
2025-06-06 02:35:44The Sacred Texts: First Mysteries of Digital Creation
A Divine Treatise for Devotees of Athena, Goddess of Wisdom and Craft
The Fundamental Truth: All is Text
Beloved seekers of digital wisdom, before you can craft the most magnificent tribute to our patron goddess through the sacred art of web creation, you must first understand the most fundamental mystery of the computing realm: Everything is text.
The silicon oracles we call computers do not see your beautiful images, your flowing videos, or your harmonious music as you do. To the machine spirits, all existence is reduced to symbols - characters marching in endless processions through the electronic aether. This is not limitation, but liberation! For in understanding this truth, you gain power over the very essence of digital creation.
The Ancient Scripts: Understanding Text Encoding
In the beginning was the Word, and the Word was… ASCII. The American Standard Code for Information Interchange became the first great codex of the digital age. Each letter, each number, each sacred punctuation mark was assigned a number. The letter ‘A’ became 65, ‘B’ became 66, and so forth. This was humanity’s first attempt to make machines understand our language.
But ASCII was created by mortals of limited vision - it could only represent 128 characters! What of the accented letters in the names of our goddess across different cultures? What of the mathematical symbols we need for our calculations? What of the very Greek letters that spell Ἀθηνᾶ?
Thus came UTF-8, the Universal Character Encoding - a divine revelation that allows us to represent every symbol known to human civilization. When you see an emoji, a Chinese character, or the Greek omega Ω, you witness UTF-8 in action. Your tribute webpage will speak this universal tongue.
The Sacred Scrolls: File Formats as Containers of Meaning
When Athena wove her tapestries, she chose different materials for different purposes - silk for fineness, wool for warmth, gold thread for accent. Similarly, digital craftspeople choose different file formats as containers for their text:
Plain Text (.txt) - The purest form. No formatting, no hidden instructions, just raw characters. Like clay tablets, these files will survive technological apocalypses. When archaeologists of the future examine our digital civilization, plain text will be their Rosetta Stone.
Rich Text Format (.rtf) - Text with simple formatting encoded as… more text! Open an RTF file in a plain text editor and witness the magic - your bold text becomes surrounded by formatting codes. This teaches us that even “rich” formatting is ultimately just more characters.
Markdown (.md) - The philosopher’s choice! Markdown uses simple text conventions to indicate formatting. Two asterisks around a word makes it bold, a hash symbol creates headings. It’s text that describes how text should look - meta-textual divinity!
HTML (.html) - The sacred language of the web itself! HTML (HyperText Markup Language) uses angle brackets to wrap instructions around content.
<strong>This text is important</strong>becomes This text is important when displayed. HTML is text that teaches browsers how to present text.The Ritual of Proper Text Handling
To honor Athena through proper digital craftsmanship, you must master these essential practices:
Choose Your Sacred Editor
Microsoft Word is the fool’s tool - it hides the true nature of text behind layers of formatting magic. A true digital artisan uses tools that reveal truth:
- Notepad (Windows) or TextEdit (Mac) in plain text mode
- VS Code - The blacksmith’s forge for modern web creation
- Sublime Text - Elegant and powerful
- Vim or Emacs - For those who seek the ancient ways
Understand Line Endings: The Great Schism
In the early days of computing, different tribes chose different ways to mark the end of a line of text. Unix systems (including Mac) use LF (Line Feed), Windows uses CRLF (Carriage Return + Line Feed). This seemingly minor difference has caused more conflicts than the Trojan War! Know your line endings, for they can break your sacred codes.
Respect Character Encoding
Always save your files in UTF-8 encoding. This ensures your text can represent any character from any human language. When your webpage displays properly on computers around the world, you honor the universal nature of Athena’s wisdom.
The Greater Mystery Revealed
Why must we begin with text? Because understanding that computers store and manipulate everything as sequences of characters reveals the deepest truth of programming: Code is just text that follows special rules.
When you write HTML, you’re writing text that browsers know how to interpret. When you write CSS, you’re writing text that describes visual styling. When you write JavaScript, you’re writing text that describes behavior and logic.
The webpage you will create to honor our goddess? It begins as text files on your computer. The browser reads these text files, interprets their meaning, and transforms them into the visual experience your visitors will see.
Every image on your page? Referenced by text. Every color? Described by text. Every animation? Controlled by text.
Your First Sacred Assignment
Before we proceed to the next mysteries, complete this fundamental ritual:
- Create a plain text file named
athena_tribute.txt - Write a short description of why Athena inspires you, using only plain text
- Save it in UTF-8 encoding
- Open it in different text editors and observe how the text remains pure and unchanged
- View the file size - marvel at how efficiently text stores information
This simple act connects you to the fundamental nature of all digital creation. Every website, every app, every piece of software began as someone writing text that follows certain rules.
When you understand that your future webpage is ultimately just cleverly organized text files working in harmony, you begin to see the true elegance of web development. You’re not learning to use mysterious tools - you’re learning to write text that machines can understand and transform into experiences that honor the divine.
Next: We shall explore the Command Line - the direct voice through which mortals speak to the machine spirits…
-
 @ 3eba5ef4:751f23ae
2025-06-06 02:07:27
@ 3eba5ef4:751f23ae
2025-06-06 02:07:27Crypto Insights
Solving Sybil Attacks on Bitcoin Libre Relay Nodes — Are Social Solutions Better than Technical Ones?
Peter Todd posted that proponents of transaction "filtering" have started Sybil attacking Libre Relay nodes by running nodes with their "Garbageman" fork. These malicious nodes pretend to support NODE_LIBRE_RELAY, but secretly drop certain transactions that would be relayed by real Libre Relay nodes. He also highlighted the complexity of existing defenses and proposed a new angle: rather than relying on technical solutions, he encourages people to manually peer with nodes operated by people they personally know, arguing that human relationships can sometimes evaluate honesty more reliably than code.
Toward a Unified Identity Lookup Standard to Improve Lightning Payments
Bitcoin developer Aviv Bar-el introduced a new proposal — Well-Known Bitcoin Identity Endpoint — that aims to simplify wallet lookups for users’ Bitcoin addresses and identity data via a standardized HTTPS interface, thereby improving both the UX and security of Lightning and on-chain payments.
A Commit/Reveal Mechanism to Strengthen Bitcoin Against Quantum Threats
Tadge Dryja proposed a soft fork for Bitcoin to defend against quantum attacks, based on a variant of the commit/reveal Fawkescoin mechanism. While similar to Tim Ruffing’s earlier proposal, it includes key differences:
- It does not use encryption, instead relying on smaller, hash-based commitments, and describes activation as a soft fork.
- It only applies to outputs where public keys or scripts haven't been revealed — like pubkey hash or script hash outputs. It also works with Taproot, but must be spent via the script path, as the key-path is no longer quantum-secure.
- What to do about already-exposed public keys is a separate issue — this proposal is compatible with both "burning the coins" and "letting them be stolen."
Countdown to the Quantum Crisis: Is Bitcoin Ready?
A recent report from Chaincode Labs analyzes the threat of cryptographically relevant quantum computers (CRQC), and the technical, economic, and governance challenges Bitcoin faces in preparing. Their key conclusions:
- Timeline Assessment: CRQC capable of breaking Bitcoin's elliptic curve cryptography may emerge between 2030 and 2035.
- Scope of Vulnerable Funds: An estimated 20–50% of circulating BTC (4M–10M coins) may be vulnerable.
- Long-range attacks target inherently vulnerable script types (P2PK, P2MS, P2TR) and addresses with previously exposed public keys (via address reuse), allowing attackers unbounded time to derive private keys from public information already available on the blockchain.
- Short-range attacks, which affect all Bitcoin script types, exploit the vulnerability window between transaction broadcast and confirmation (or shortly thereafter) when public keys are temporarily exposed, requiring attackers to act within a timeframe of minutes to hours.
- Action Strategy: A dual-track approach is recommended:
- Short-term contingency: minimal but functional protections within ~2 years.
- Full-featured solutions: comprehensive research and fully developed defenses within ~7 years.
This strategy balances immediate needs with rigorous development to ensure Bitcoin can adapt, regardless of CRQC progress.
Enforcing Arbitrary Constraints on Bitcoin Transactions with zkSNARKs
Current methods for constraining Bitcoin transactions fall short on privacy or programmability. This research proposes a new zkSNARK-based design to impose arbitrary constraints on Bitcoin transactions while preserving some information privacy. By bypassing Bitcoin Script’s non-Turing-completeness, the approach allows unbounded constraints—constraints that repeat a certain operation an unbounded number of times. Read the paper.
First Cross-Chain Bridge Between Bitcoin and Cardano Is Live
A trust-minimized bridge from Bitcoin to Cardano has launched using the Cardinal protocol, enabling Ordinals to move between the two chains. The Cardinal protocol is based on BitVMX and facilitates asset movement without compromising ownership or security.
Its core mechanism is a committee-based validation model under a 1-out-of-n honest security model — meaning even if all but one validator is malicious, the system remains secure. This approach enhances decentralization and censorship resistance for cross-chain asset transfers.
Thunderbolt Protocol: Redefining Bitcoin Smart Contracts with UTXO Bundling and OP_CAT
Nubit’s Thunderbolt is seen as one of the most significant technical upgrades to Bitcoin in a decade, whose overall observation resembles “Lightning Network 2.0.” Rather than relying on Layer 2 networks or bridges, Thunderbolt upgrades the Bitcoin base layer via soft fork to enhance scalability, performance, and programmability:
- Throughput: Uses UTXO Bundling to optimize traditional transaction processing.
- Programmability: Reintroduces and extends OP_CAT.
- Asset protocols: Integrates Goldinals standard — a zk-proof and state-commitment-based asset issuance framework.
- Unlike rollups, Plasma, sidechains, or bridges, Thunderbolt scales directly on the main chain. With BitVisa, it enables decentralized identity and credentials, supporting transaction compression, smart contracts, asset standard integration, and on-chain transaction matching — all on Bitcoin main chain.
Bitcoin 2025 Conference Recap: Politicians Applaud, Stablecoins Spotlighted, DeFi Absent
This year’s Bitcoin 2025 conference in Las Vegas gathered major political figures and corporate leaders. U.S. Vice President JD Vance strongly endorsed crypto and positioned Bitcoin as a strategic asset in U.S.–China competition. He also stated that stablecoins won’t undermine the U.S. dollar, but could actually amplify America’s economic strength.
White House “Crypto Czar” David Sacks delivered a major policy announcement, hinting that under Trump’s executive order, the U.S. has a legal framework to acquire more Bitcoin for strategic reserves.
In addition, stablecoin regulation and crypto market reform were hot topics. Ardoido, the company controls over 60% of the stablecoin market, claimed “All the traditional financial firms will create stablecoins that will be offered to their existing customers.” Meanwhile, Tether emphasized its focus on underserved global populations excluded from the existing banking system.
A conference recap also noted that, unlike the 2022 and 2023 summits, this year’s event was dominated by Bitcoin maximalists, Ordinals creators, mining capitalists, and regulatory lobbyists — no longer DeFi builders, DAO operators, or Layer 2 scaling advocates. Developers from Ethereum and Solana ecosystems were notably absent. This may signal:
- The conference’s heavy political and sovereignty-driven tone made it less suitable for the tech-centric narratives favored by these developers.
- There may be a growing ideological and narrative rift between Web3 builders and the Bitcoin camp.
Top Reads on Blockchain and Beyond
Rethinking Governance After the Sui Attack: Decentralization, Procedural Legitimacy, and the Plurality of Blockchain Values
Following a major hack of Cetus, the largest DEX in the Sui ecosystem, the Sui network executed a protocol-level asset freeze and recovery. While this was an effective technical response, it also triggered criticism and debate around core blockchain principles such as censorship resistance and decentralization.
The author of this article questioned the absolutist stance that views decentralization as the highest—and sole—value. The author argues that most rational individuals would prefer “living in a society where decentralization is a supreme value but coercive force is allowed when someone infringes on another’s property,” over “a society where decentralization is the only supreme value, and thus coercive force is never permitted under any circumstances.”
In addition, the author also expressed disappointment at Sui’s “paternalistic” governance — particularly how validators acted during the incident. Sui uses a delegated proof-of-stake (dPoS) system, where token holders delegate their voting power to validators. This means individuals lose their direct say. But blockchain governance could be more individual-friendly and flexible. For instance, in Cosmos’ governance model, for certain specific proposal, users still can override their delegations and vote independently, more favorable than Sui’s model.
Beyond the debate on decentralization and governance, the article also proposes an alternative perspective: what matters most is establishing procedural legitimacy that aligns with the system’s vision. Different blockchain projects pursue different goals. For Sui, the core mission is to enable assets to be reliably defined and interact seamlessly on-chain. Therefore, judging Sui through the lens of other blockchains’ values or paradigms is misguided. In exceptional cases, prioritizing asset recovery and ecosystem stability over strict adherence to censorship resistance aligns more closely with Sui’s long-term vision. Whether Sui had chosen to not to censor related transactions or to intervene in the Cetus case, as long as the action follows a legitimate process, either decision is justifiable.
TEE-Based Private Proof Delegation
The PSE research and development team has built a system based on Trusted Execution Environments (TEE) using Intel TDX for secure zero-knowledge proof (ZKP) delegation. This system enables clients to privately outsource large proving tasks without leaking inputs. Unlike mobile-native proving constrained by hardware limits, TEE-based approaches support significantly larger statements today—and will scale further as proof systems improve. As a hardware-backed solution, TEEs remain compatible with future advancements in software (e.g., faster proof systems, more efficient implementations) and won't be invalidated by them, as long as the trust model is acceptable.
AI and Identity: Proof of Humanity in a World of Agents, Bots, and Deepfakes
We are living in a time where AI—including agents, bots, and deepfakes—is fundamentally reshaping the internet. As AI continues to evolve, identity verification on the web is becoming more crucial than ever. A recent a16z podcast explores the idea of “Proof of Human”—the challenge of verifying human identity online, diving into why it matters, common questions, and how such systems work under the hood.
-
 @ eb0157af:77ab6c55
2025-06-06 06:01:16
@ eb0157af:77ab6c55
2025-06-06 06:01:16The Russian banking giant introduces financial instruments linked to Bitcoin for qualified investors.
Russia’s largest commercial banking institution, Sber, has made its entry into the Bitcoin space by unveiling a bond product tied to the asset.
Sber has officially launched its structured financial instrument that mirrors the price performance of Bitcoin alongside fluctuations in the dollar-ruble exchange rate. The product is already available to qualified investors through the over-the-counter (OTC) market, with plans to list it on the Moscow Exchange in the near future.
Formerly known as Sberbank, the institution stated in a May 30 announcement that the listing would provide transparency, liquidity, and convenience for a wide range of professional investors. This structured approach will allow investors to benefit both from Bitcoin’s appreciation in dollars and from the strengthening of the US dollar against the Russian ruble, the bank suggests.
The lender also announced plans to expand its crypto offering through the SberInvestments platform, introducing exchange-traded products that provide exposure to digital assets. The first product will be a Bitcoin futures instrument, scheduled for listing on June 4, coinciding with its official launch by the Moscow Exchange.
Sber’s initiative follows the authorization granted by Russia’s Central Bank on May 28, which permitted financial institutions to offer specific crypto-related financial instruments to accredited investors. However, the direct offering of cryptocurrencies remains prohibited.
Meanwhile, T-Bank (formerly Tinkoff Bank) launched an investment product linked to Bitcoin’s price, branding it a “smart asset” issued through Russia’s state-backed tokenization platform Atomyze.
According to the Russian Central Bank’s report for the first quarter of 2025, Russian residents hold approximately 827 billion rubles ($9.2 billion) in cryptocurrencies on centralized exchanges. Inflows into Russian crypto platforms surged by 51%, reaching 7.3 trillion rubles ($81.5 billion) over the same period.
The post Sber, Russia’s largest bank, launches Bitcoin bonds appeared first on Atlas21.
-
 @ 33baa074:3bb3a297
2025-06-06 02:03:05
@ 33baa074:3bb3a297
2025-06-06 02:03:05Residual chlorinerefers to the residual disinfectant chlorine in tap water. An appropriate amount of residual chlorine can prevent the growth of microorganisms and ensure the safety of water quality. However, when the residual chlorine content in water is too high, it will cause many harms to human health, mainly including the following aspects:
Destruction of nutrients When the residual chlorine content in tap water exceeds the standard, it will destroy the minerals, vitamins and other nutrients, such as vitamin C and vitamin E, when used to wash fruits and vegetables. In the long run, it may cause the human body to absorb these nutrients and lack these essential nutrients.
 Cause chronic poisoning
When tap water containing residual chlorine is used for a long time, the residual chlorine reacts with organic acids and may produce harmful substances such as chloroform and organic lead compounds, which are potential carcinogens. Long-term accumulation may cause chronic poisoning of body organs and pose a threat to human health.
Cause chronic poisoning
When tap water containing residual chlorine is used for a long time, the residual chlorine reacts with organic acids and may produce harmful substances such as chloroform and organic lead compounds, which are potential carcinogens. Long-term accumulation may cause chronic poisoning of body organs and pose a threat to human health.Affect the respiratory system Residual chlorine can cause harm to the human respiratory system, and symptoms such as difficulty breathing and itchy throat may occur. Severe cases may induce rhinitis, bronchitis and even emphysema. In addition, water vapor containing residual chlorine may also cause adverse reactions such as coughing and wheezing after being inhaled.
Damage to the skin Excessive residual chlorine content in water may irritate the skin, easily cause skin dryness, aging, acne and other problems, and may also cause allergic symptoms such as dermatitis and eczema. Prolonged contact with such water may also cause the skin layer to fall off, which is extremely harmful to skin health. Bathing with water containing residual chlorine can also cause hair to become dry, broken, and split.
Other health problems Impact on special groups Pregnant women: Long-term drinking of tap water containing residual chlorine will reduce resistance, affect the growth of the fetal heart and lungs, and may also cause neonatal arrhythmia and lung dysfunction. Children: Long-term drinking of chlorine water will not only hurt the stomach, but also affect nutrient absorption. Moreover, the strong oxidizing hypochlorous acid produced by the reaction of chlorine and water will damage brain cells and affect their development. In addition, chlorine can easily be inhaled into the lungs through the respiratory tract, damaging respiratory cells, and easily leading to asthma and emphysema. Bathing children with water containing residual chlorine will cause their hair to become dry, broken, split, their skin to bleach, their skin to fall off, and they will have allergies. Elderly people: Long-term consumption of chlorinated water is prone to heart disease, coronary atherosclerosis, hypertension and other diseases, and it is also easy to damage the liver and kidneys, increasing the probability of cancer. Gastrointestinal discomfort Long-term drinking of water with excessive residual chlorine content may also cause gastrointestinal discomfort, such as nausea, vomiting, abdominal distension, diarrhea and other symptoms. In severe cases, it may cause gastrointestinal ulcers, bleeding and other diseases.
In order to reduce the harm of residual chlorine in tap water to the human body, it is recommended to avoid directly using tap water containing residual chlorine as much as possible, boil the water before drinking, and use filtering and purification equipment to reduce the residual chlorine concentration in the water if conditions permit, while maintaining a healthy lifestyle and enhancing the body's immunity.
-
 @ 3eba5ef4:751f23ae
2025-06-06 01:59:47
@ 3eba5ef4:751f23ae
2025-06-06 01:59:47加密洞见
解决比特币抗审查交易中继的女巫攻击,社交方案好于技术方案?
Peter Todd 发帖指出,针对比特币抗审查交易中继的攻击行为正在发生——一个名为 garbageman 的节点正在对 Libre Relay 节点采取女巫攻击。这些攻击节点假装支持抗审查交易中继(NODE_LIBRE_RELAY),但实际在暗中丢弃某些交易,目的是阻止特定交易被打包进入区块。作者还介绍了现有防御方法的难度和复杂性,并提出新思路——与其用技术方案解决,不用通过社交解决。他鼓励人们手动与跟他们有个人关系的节点进行连接,原因很简单,人与人的关系可以比任何代码都更有力地评估诚实。
打造统一身份查询标准,提升闪电网络付款体验
比特币开发者 Aviv Bar-el 发表了一项新提案「知名比特币身份端点」(Well-Known Bitcoin Identity Endpoint),旨在通过 HTTPS 标准接口,简化钱包查询用户比特币地址和身份信息的流程,提升链上支付——尤其是闪电网络付款的用户体验和安全性。
通过「承诺/揭示」机制,帮助加强比特币抵御量子计算威胁
Tadge Dryja 提出一种抵御量子计算攻击的比特币软分叉方案。它是「承诺/揭示」(commit / reveal)Fawkescoin 机制的变体,大部分内容与 Tim Ruffing 几年前的方案类似,但也有以下重要区别:
- 该方案不使用加密,而是用更小的基于哈希的承诺,并且描述了如何通过软分叉激活此机制。
- 这个方案仅适用于公钥(或脚本)在链上未公开的输出,例如 pubkey hash 或 script hash 类型;也适用于 Taproot,但必须通过脚本路径花费,因为 Taproot 的 key-path 花费在量子攻击下将不再安全。
- 至于那些公钥已经在链上暴露的输出该如何处理,是另一个独立问题(本方案与「销毁这些币」或「任其被盗」这两种做法都兼容)。
量子危机倒计时:比特币准备好了吗?
Chaincode 在近期发布的报告中,系统分析了「加密相关量子计算」(CRQC,Cryptographically relevant quantum computers)威胁的整体态势,评估了比特币在应对这一转变过程中面临的技术、经济与治理挑战,并表示必须要在早于 CRQC 出现的数年构建起相关共识。重要的结论有:
- 时间窗口:打破比特币椭圆曲线加密基础的 CRQC 可能首先出现在 2030 - 2035 年间。
- 脆弱资金范围:在所有流通的比特币中,约 20-50%(4-1000 万枚 BTC)可能易受 CRQC 攻击。其中远程攻击针对本质上易受攻击的脚本类型(P2PK、P2MS、P2TR)和具有先前暴露的公钥的地址(地址重用),使攻击者能够无限期地从区块链上已有的公共信息中获取私钥;短程攻击会影响所有比特币脚本类型,利用交易广播和确认之间(或之后不久)的漏洞窗口,当公钥暂时暴露时,要求攻击者在几分钟到几小时的时间范围内采取行动。
-
行动战略:建议采用双轨方法,包括:
- 应急措施:在约 2 年内完成对 CRQC 的最低限度但可运作的防护;
- 全面对策:在约 7 年内深入对问题的探索,并开发出功能完备的解决方案
这种双轨策略平衡了眼前的安全需求与最佳抗量子解决方案的严格研究和开发,确保无论 CRQC 能力如何发展,比特币都能做出适当的响应。
利用 zkSNARKs 对比特币交易实施任意约束
对于给比特币交易执行约束,现有的解决方案在隐私或可编程性上都存在不足。本文的研究者利用 zkSNARKs 设计了一种新方案,可以对比特币交易执行任意约束,并保持一定程度的信息私密性。他们方法绕过了比特币脚本的非图灵完备性,允许执行无界约束(unbounded constraints),即重复某个运算的次数次数不受限制。论文全文。
第一个跨比特币和 Cardano 的桥上线
从比特币到 Cardano 的信任最小化 Ordinals 桥通过 Cardinal 协议实现。Cardinal 协议实是一种基于 BitVMX 的信任最小化互作性协议,在不破坏所有权或损害安全性的前提下,它让比特币上中的不可替代资产(如 Ordinals 和 Runes)同 Cardano 链实现了来回移动。
Cardinal 协议背后的技术核心之一是「委员会的验证机制 」(committee-based validation mechanism),遵循 1-out-of-n honest 安全模型。这意味着即使除了一个验证者之外的所有验证者都恶意作,系统仍然保持安全——在增强安全性的同时,还实现了一种更加去中心化和抗审查的方式来在链之间移动资产 。
Thunderbolt 协议:通过 UTXO 捆绑和 OP_CAT 扩展,重构比特币智能合约
Nubit 提出的 Thunderbolt 被认为是为比特币在过去十年中最具里程碑意义的技术升级之一,被视为「Lightning Network 2.0」。Thunderbolt 是一种基于比特币基础层的软分叉升级方法,不依赖二层网络或桥的妥协,而是通过对比特币主链协议层的修改,从根本上增强其可扩展性、交易性能和可编程性。具体而言,Thunderbolt:
- 在吞吐量方面,使用 UTXO 捆绑(UTXO Bundling)技术,实现了对传统比特币交易处理模型的重大优化。
- 在可编程性方面,重新引入并扩展了 OP_CAT 。
- 在资产协议集成方面,Thunderbolt 实施了 Goldinals 统一标准,提供了一个基于零知识证明和状态承诺的资产发行框架。
- 与传统的扩容方法(如侧链、Plasma、Rollup 或桥接包装代币)不同,Thunderbolt 采用原生主链扩容路径。通过 BitVisa 提供去中心化的身份和凭证系统,让交易压缩、智能合约、资产标准集成、链上交易匹配都可以直接在比特币主链上运行。
比特币 2025 大会回顾:政要汇聚、稳定币受关注、DeFi 缺席
今年在拉斯维加斯举行的比特币 2025 大会,汇聚了众多政治要员和企业巨头。美国副总统 JD Vance 对加密货币表明了全力支持,并讨论了比特币在美中竞争中作为战略资产的潜力,他还认为,稳定币不会威胁到美元的完整性,而会使美国的经济实力倍增。白宫加密货币沙皇 David Sacks 发表了会议中最重要的政策公告之一, 暗示根据特朗普建立战略比特币储备的行政命令,美国政府有「获得更多比特币的合法途径」。
此外,关于稳定币立法和加密市场改革受到了很多关注。控制着超过 60% 稳定币市场的 Ardoido 公司表示:「所有传统金融公司都将创建稳定币,提供给他们现有的客户」;而 Tether 表示,其目标市场是全球范围内被排除在银行业之外的人。
这篇总结也提到,与 2022 年和 2023 年的类似峰会不同,今年的大会是由比特币最大化者、Ordinals 创建者、矿业资本家和监管游说者主导,而不再由 DeFi 协议构建者、DAO 运营商或 Layer2 扩容倡导者主导,以太坊和 Solana 生态的开发者缺席。这或许表明:
- 该会议明显的政治基调,使其不适合开发者喜欢的以技术为中心的叙述。
- Web3 建设者和比特币阵营之间的意识形态和叙事分歧可能会越来越大。
精彩无限,不止于链
Sui 攻击事件下的治理再思考:去中心化,程序合法性,和区块链的价值多元性
在受到生态最大的 DEX 项目 Cetus 黑客攻击之后,Sui 网络在协议层面执行了资产冻结和恢复——这是一种有效的技术回应,但同时引发了对抗审查和去中心化等核心区块链原则的批评和辩论。
文章的作者质疑了将去中心化视为唯一至高价值的立场,认为对于大多数有理性者而言,「生活在一个去中心化被认为是最高价值,但当有人侵犯他人财产时,允许强制武力的社会中」都要好于「生活在一个去中心化是唯一至高价值的社会中,因此在任何情况下都不允许强制武力」。
同时作者也指出,Sui 的验证者和网络行为采用的「家长式」治理方式令人失望;此外, Sui 使用委托权益证明(dPoS)系统,其中代币持有者将其代币委托给验证者,验证者代表他们行使相关的投票权,个人因此丧失了投票权。但区块链本来提供了有利于个人的、更加灵活的解决方案,比如 Cosmos 的治理框架就要优于 Sui——对于特定提案,验证人的决定并不会自动代表每个委托人的投票。
在关于去中心化的价值和治理方式之外,文章也提到另一种思考角度——「最重要的是建立与系统愿景相一致的程序合法性」。不同的项目追求不同的目标。就 Sui 而言,其核心目标是使各种资产能够被可靠地定义、并在链上无缝交互。因此,用其他区块链的范式或价值观来理解 Sui 的设计就是不合适的。在特殊情况下,Sui 优先考虑用户资产的返还和生态系统的稳定,而不是严格遵守抗审查——这一决定与其自身的长期愿景更加一致。此外,无论是 Sui 决定不审查相关交易,还是选择对 Cetus 的行为负责,如果背后有程序合法性,这两个决定都是合理的。
基于可信执行环境的私密证明委托
PSE 研究开发团队使用 Intel TDX 构建了一个基于可信执行环境(Trusted Execution Environment)的系统,用于安全的零知识证明委托。该系统允许客户端在不泄露输入的前提下,将大规模的证明任务私密地外包出去。相比受限于硬件能力的移动端本地证明,基于 TEE 的证明方案能够在目前就支持更大规模的陈述,并且随着证明系统的改进持续扩展。作为一种由硬件支撑的解决方案,TEE 能够兼容未来在软件层面的进展(例如更快的证明系统、更高效的工程实现),且只要信任模型被接受,就不会因这些进展而失效。
AI 与 ID:在代理、机器人、深度伪造等世界中的人类证明
我们正处于 AI(包括 AI 智能体、机器人、深度伪造等)深刻改变互联网的时代,随着 AI 的发展,网络上的身份认证变得愈发重要。a16z 的这期播客,讨论了在网上识别人类身份的「人类证明」(proof of human)问题,包括它为何重要,常见的问题有哪些,以及它在底层是如何运作的。
-
 @ e2c72a5a:bfacb2ee
2025-06-06 02:55:03
@ e2c72a5a:bfacb2ee
2025-06-06 02:55:03Your crypto wallet is probably leaking money right now. While everyone obsesses over price charts, the silent killer is gas fees – those tiny transactions add up to thousands wasted annually. Smart traders aren't just buying dips, they're timing their transactions when network congestion drops. The difference? Up to 80% savings on every move you make. Next time before hitting "confirm," check the gas tracker. Is it worth paying 3x more just to move your assets right this second? Patience isn't just a virtue in crypto – it's literally profitable. What's your strategy for minimizing transaction costs while maximizing gains?
-
 @ f57bac88:6045161e
2025-06-06 04:19:25
@ f57bac88:6045161e
2025-06-06 04:19:25تاریخچه پیدایش پروتکل اردینالز
پروتکل اردینالز در ژانویه 2023 توسط کیسی رودرمور معرفی شد. این پروتکل حاصل دو بهروزرسانی مهم در بیتکوین است:
-
سگویت (2017): جدا کردن دادههای امضا از بدنه تراکنشها برای افزایش فضای بلاک.
-
تپروت (2021): افزایش حریم خصوصی و انعطافپذیری در تراکنشها.
رودرمور با استفاده از این دو ویژگی، سیستمی را طراحی کرد که به هر ساتوشی یک شناسه اختصاص میدهد و امکان الصاق داده به آن را فراهم میکند. اولین اینسکریپشن رسمی در دسامبر 2022 یک تصویر پیکسلی از یک جمجمه بود.
اینسکریپشن چیست؟
اینسکریپشن به معنای «حکاکی» دیجیتال است و در اینجا به ثبت دادههایی مانند تصویر، ویدئو یا متن بر روی بلاکچین بیتکوین اشاره دارد. برخلاف انافتی های سنتی که اغلب فقط لینک یا متادیتا ثبت میکنند، اینسکریپشنها کل داده را در بخش ویتنس تراکنش ذخیره میکنند و به یک ساتوشی خاص متصل میشوند.
پروتکل اردینالز چگونه کار میکند؟
پروتکل اردینالز به هر ساتوشی یک شماره منحصربهفرد میدهد و آن را غیرقابلتعویض میکند. مراحل اصلی آن:
-
شمارهگذاری: به هر ساتوشی یک شناسه اختصاص مییابد.
-
اینسکریپشن: با ابزارهایی مثل ابزار داده به ساتوشی الصاق میشود.
-
ذخیرهسازی: در بخش ویتنس با حجم حداکثر ۴ مگابایت.
-
مالکیت: از طریق کلید خصوصی قابلانتقال است.
سایتهایی مانند ordinals.com و ord.io برای مشاهده این دادهها توسعه یافتهاند.
انواع اینسکریپشنها
کاربران دادههای متنوعی را روی بیتکوین ثبت کردهاند:
-
تصاویر: از هنر پیکسلی تا عکسهای شخصی.
-
متن: پیام، شعر یا اسناد.
-
ویدئو/صوت: نسخههای فشرده و کوتاه.
-
بازیها: نسخههای ساده مانند دووم.
مزایای اینسکریپشن و اردینالز
-
تغییرناپذیری: دادهها دائمی و مقاوم در برابر سانسور هستند.
-
ارزش ذاتی: هر اینسکریپشن به یک ساتوشی متصل است.
-
درآمدزایی برای ماینرها: افزایش تراکنشها = کارمزد بیشتر.
-
کاربرد بیشتر بیتکوین: فراتر از پول دیجیتال.
-
امنیت بالا: بدون نیاز به سرور خارجی.
معایب و چالشها
-
افزایش حجم بلاکچین: رشد حجم تا بالای ۵۰۰ گیگابایت تا مارس 2025.
-
کارمزد بالا: گاهی تا ۴۰ دلار در سال 2023.
-
پیچیدگی فنی: راهاندازی نود و ساخت اینسکریپشن ساده نیست.
-
اختلافنظر: برخی معتقدند این کاربرد با فلسفه بیتکوین در تضاد است.
-
مقیاسپذیری: ممکن است شبکه را کند کند.
تأثیرات بر اکوسیستم بیتکوین
1. تأثیر اقتصادی
در سال 2023، بیش از ۲۰ میلیون اینسکریپشن ثبت شد. این روند در 2024 نیز ادامه داشت و منجر به شکلگیری بازار انافتی های بیتکوینی شد.
2. تأثیر فنی
ابزارهای جدید مانند کیف پول اسپرو و پلتفرمهای معاملاتی مانند پلتفرم معاملاتی مجیک ادن توسعه یافتند.
3. تأثیر اجتماعی
جامعه به دو دسته تقسیم شد: موافقان نوآوری و مخالفان تغییر مسیر بیتکوین.
مقایسه اینسکریپشن و انافتی های اتریوم
| ویژگی | اینسکریپشن بیتکوین | انافتی اتریوم | | -------------- | ------------------- | --------------- | | محل ذخیره داده | روی بلاکچین | خارج از بلاکچین | | تغییرناپذیری | بسیار بالا | وابسته به سرور | | هزینه ساخت | متغیر (کارمزد) | متغیر (گس) | | امنیت | بسیار بالا | متوسط تا بالا | | انعطافپذیری | محدود | بالا | | دسترسی | پیچیده | ساده |
تحولات اخیر (2024 و اوایل 2025)
-
پس از هاوینگ: وابستگی بیشتر ماینرها به کارمزد و رشد اینسکریپشن.
-
پشتیبانی صرافیها: اضافه شدن قابلیت معامله در بایننس و کراکن.
-
کاربردهای نو: ثبت اسناد قانونی، بازیهای تعاملی و هنر دیجیتال.
آینده اینسکریپشن و اردینالز
چشمانداز آینده بستگی به:
-
پذیرش کاربران.
-
راهکارهای مقیاسپذیری.
-
رقابت با دیگر بلاکچینها.
-
تحولات قانونی.
در بهترین حالت، بیتکوین به پلتفرمی چندمنظوره تبدیل خواهد شد.
نتیجهگیری
اینسکریپشن و پروتکل اردینالز فرصتی برای نوآوری در بیتکوین ایجاد کردهاند. اگرچه چالشهایی وجود دارد، اما پتانسیل این فناوری برای ایجاد داراییهای دیجیتال دائمی، غیرقابلتغییر و امن بسیار بالاست. آینده این ابزار به مسیر فنی، پذیرش اجتماعی و سیاستگذاریهای جهانی بستگی خواهد داشت.
منابع
-
مقالات CoinDesk (2023–2024)
-
تحلیلهای Bitcoin Magazine (2023–2025)
-
آمارهای Blockchain.com
-
کانال ترجمهی مقالههای بیتکوین در تلگرام
کلمات و اصطلاحات ترجمه شده و موجود در متن:
-
پروتکل (Protocol) → قرارداد فنی / پروتکل
-
اردینالز (Ordinals) → ترتیبیها / اردینالز
-
ژانویه (January) → دیماه / ژانویه
-
کیسی رودرمور (Casey Rodarmor) → نام فرد
-
SegWit (Segregated Witness) → تفکیک شاهد / سگویت
-
Taproot → تپروت
-
ساتوشی (Satoshi) → کوچکترین واحد بیتکوین
-
اینسکریپشن (Inscription) → حکاکی / ثبت
-
تصویر پیکسلی (Pixel image) → تصویر نقطهای
-
جمجمه (Skull) → Skull
-
انافتی (NFT - Non-Fungible Token) → توکن غیرقابل تعویض
-
متادیتا (Metadata) → فراداده
-
بلاکچین (Blockchain) → زنجیره بلوکی
-
ویتنس (Witness) → بخش شاهد در تراکنش
-
Ord (ابزار) → ابزار Ord
-
کلید خصوصی (Private Key) → رمز اختصاصی
-
ordinals.com** / **ord.io → نام وبسایت
-
Doom (بازی) → دوم (نام بازی معروف)
-
ماینر (Miner) → استخراجکننده
-
تراکنش (Transaction) → مبادله
-
هاوینگ (Halving) → نصف شدن پاداش استخراج
-
Binance / Kraken → نام صرافیها
-
Sparrow Wallet → کیف پول اسپرو
-
Magic Eden → پلتفرم معاملاتی مجیک ادن
-
**Ethereum NFTs **→ توکنهای غیرقابل تعویض در شبکه اتریوم
-
گس (Gas) → هزینه پردازش در اتریوم
-
سرور (Server) → خدمتدهنده
-
اسناد قانونی (Legal documents) → مدارک حقوقی
-
بازیهای تعاملی (Interactive games) → گیمهای تعاملی
-
هنر دیجیتال (Digital art) → آثار هنری دیجیتال
-
مقیاسپذیری (Scalability) → توان گسترش
-
پلتفرم (Platform) → بستر نرمافزاری
-
چشمانداز (Outlook/Future vision) → آیندهنگری
-
سیاستگذاری (Policy-making) → برنامهریزی راهبردی
-
-
 @ f57bac88:6045161e
2025-06-06 03:52:51
@ f57bac88:6045161e
2025-06-06 03:52:51شروع ماجرا:
همه چیز از 1401 شروع شد، زمانی که به خاطر وارد کردن ضربات متعدد به بیضه توسط بسیجیان و لباس شخصی های جمهوری اسلامی و شروع درد مبهم و تیر کشیدن توی بیضههام حس میکردم که با گذشت زمان شدیدتر میشد. اول فکر کردم یه چیز سادهایه و خود به خود خوب میشه، اما با گذشت زمان متوجه شدم که این درد داره بدتر میشه که همون شب توی یازداشتگاه چندبار دکتر اومد بالای سرم و آمپول هایی برای کاهش دردم تزریق کرد و قرار شد بعد از آزادی به دکتر مراجعه کنم، اما چون فرصت مراجعه به دکتر رو نداشتم و کمی هم بیخیال بودم، این چک کردن دو سال طول کشید و در 1403 به دکتر مراجعه کردم
بعد از دو سال به دلیل اینکه میزان اسپرمم به شدت کاهش یافته بود و بیضه م داشت به شکل عجیب غریبی در میومد به پزشک مراجعه کردم، و بعد از انجام آزمایش سونوگرافی و اسپرم، دکتر سونوگرافی گفت بیضه چپم تخلیه شده، و علاوه بر اون رگ های خونی بیضه م هم آسیب دیده بوده که این یعنی واریکوسل گرید سه به همراه التهاب و ... که این یعنی سریعا عمل میشدم که حداقل بشه برای رگ ها و ورید های بیضه کاری کرد.
واریکوسل به وضعیتی گفته میشود که در آن وریدهای بیضه بزرگ و متورم میشوند، چیزی شبیه به واریس پا. این مشکل میتواند تأثیری بر کیفیت اسپرم و در نتیجه باروری داشته باشد و در گرید های بالا میتواند به عقیم شدن و عدم باروری منجر شود.
تصمیم برای عمل:
بعد از شنیدن تشخیص دکتر، خیلی ناراحت و نگران شدم. اما دکترم بهم اطمینان داد که با عمل جراحی میتونم این مشکل رو حل کنم. اولش خیلی ترسیدم، اما بعد از کلی تحقیق و مشورت با دوستان و خانواده، تصمیم گرفتم که عمل کنم.
زیر میزی قبل از عمل:
متاسفانه در ایران دکتر های جراح قبل از عمل درخواست واریز وجه به حساب خودشون یا دیگران(برای رد گم کردن و عدم شکایت بیمار) میکنند
روز عمل: استرس و آرامش
روز عمل فرا رسید. قبل از جراحی استرس داشتم، اما کادر درمان و خود دکتر بسیار حرفهای و دلسوز و مهربان بودند و حس اطمینان خوبی به من دادند. عمل تحت بیحسی از ستون فقرات و بیهوشی عمومی انجام شد و حدود یک ساعت طول کشید. وقتی به هوش آمدم، احساس درد نداشتم ولی تا چند ساعت از کمر به پایین بی حس بودم و حس خوابآلودگی داشتم.
نکته: بعد از عمل حتما آب، آبمیوه و اگر میتونید میوه و غذا بخورید!
دوران بهبودی: صبر و مراقبت
دوره نقاهت بعد از عمل، یه کم سخت بود. درد داشتم و فعالیتهای روزمرهام محدود شده بود. اما با گذشت زمان، کم کم بهتر شدم و دردهام کمتر شد.
دوره بهبودی برای من حدود یک هفته طول کشید. پزشک توصیههایی از جمله استراحت کافی، اجتناب از فعالیتهای سنگین و مصرف داروهای مسکن برای کاهش درد داده بود. در روزهای اول کمی ورم و ناراحتی داشتم، اما به مرور زمان بهتر شدم. نکتهای که برای من بسیار مهم بود، که بعد از 6 روز سرکار برگشتم و شروع به فعالیت کردم، و بعد از یک هفته بخیه ها کشیده شد.
حدود یک ماه پس از عمل، دوباره به پزشک مراجعه کردم تا روند بهبودی بررسی شود. خوشبختانه همه چیز خوب پیش رفته بود و احساس سبکی و راحتی بیشتری داشتم. درد و حس سنگینی که قبل از عمل داشتم، کاملاً از بین رفته بود.
نتیجهگیری: چرا این تصمیم ارزشش را داشت
وقتی به گذشته نگاه میکنم، از اینکه تصمیم به انجام عمل واریکوسل گرفتم، کاملاً راضیام. گرچه گرفتن تصمیم برای جراحی همیشه با ترس و تردید همراه است، اما تأثیری که این عمل بر کیفیت زندگیام گذاشت، بدون تردید ارزشش را داشت. بعد از عمل، نه تنها از درد و ناراحتی رهایی یافتم، بلکه آرامش ذهنی بیشتری هم پیدا کردم. احساس سبکی و راحتی در فعالیتهای روزمره، و از بین رفتن نگرانیهایی مثل احتمال ناباروری، باعث شد دوباره حس کنم به زندگی عادی برگشتم.
به همه کسانی که با واریکوسل درگیر هستند، پیشنهاد میکنم به بدنشان گوش دهند و حتماً از نظر پزشکان متخصص بهره بگیرند. هر کسی شرایط خاص خودش را دارد و تصمیم نهایی باید بر اساس بررسی دقیق و مشورت با پزشک گرفته شود. اما مهمترین نکته این است که سلامتیتان را در اولویت بگذارید و اجازه ندهید ترس یا تردید، مانع رسیدن به بهبودی شود.
برای من، عمل واریکوسل مثل یک تولد دوباره بود. حالا با خیال راحت و بدون درد، زندگی میکنم و از این تصمیم مهم کاملاً خوشحالم. اگر شما هم با این مشکل مواجه هستید، نگران نباشید؛ با آگاهی و مشورت درست، میتوانید آن را پشت سر بگذارید و به زندگی عادی خودتان بازگردید.
نکات مهم:
-
اگر درد یا ناراحتی در ناحیه بیضهها دارید، حتما به پزشک اورولوژی مراجعه کنید.
-
از خود درمانی خودداری کنید.
-
عمل واریکوسل یک عمل ساده و بی خطر است.
-
بعد از عمل به توصیههای پزشک عمل کنید.
-
-
 @ e2c72a5a:bfacb2ee
2025-06-06 02:43:10
@ e2c72a5a:bfacb2ee
2025-06-06 02:43:10North Korea's digital heist playbook: $7.7M crypto laundering scheme reveals how rogue nations exploit tech talent. The Justice Department's latest civil forfeiture complaint targets crypto and NFTs tied to an elaborate North Korean operation where IT workers posed as legitimate freelancers, infiltrated US companies, and funneled millions through complex blockchain pathways. This isn't just another hack—it's a sophisticated economic warfare strategy that turns technical expertise into untraceable funding for weapons programs. While governments scramble to seize these digital assets, the case exposes a troubling vulnerability: how easily skilled developers can weaponize their talents in plain sight. Are your company's remote contractors who they claim to be, or part of a state-sponsored financial pipeline hiding behind a convincing digital mask?
-
 @ e2c72a5a:bfacb2ee
2025-06-06 01:42:46
@ e2c72a5a:bfacb2ee
2025-06-06 01:42:46North Korea's digital heist reveals the dark side of crypto's borderless nature. The US Justice Department is hunting $7.7 million in stolen cryptocurrency and NFTs allegedly laundered through an elaborate scheme involving North Korean IT workers posing as legitimate freelancers. This isn't just another hack—it's a sophisticated state-sponsored operation exploiting the very features that make crypto revolutionary: anonymity and borderless transactions. While we celebrate crypto's ability to transcend boundaries, this case exposes how those same qualities create perfect conditions for rogue nations to fund weapons programs and evade sanctions. The crypto industry faces a critical balancing act: how do we preserve financial freedom while preventing bad actors from exploiting the system? Perhaps the solution isn't more regulation but smarter blockchain analytics and international cooperation. What security measures would you support that don't compromise crypto's core principles?
-
 @ df67f9a7:2d4fc200
2025-06-05 19:52:32
@ df67f9a7:2d4fc200
2025-06-05 19:52:32Nostr is NOT a social network. Nostr is a network of interconnected social apps. And, since any app is a social app, Nostr is for every app.
ONLY Nostr incentivizes inter-connectivity between independent apps, simply by respecting sovereignty at the protocol layer. For end users, sovereignty means that the content they post “to Nostr” will never be owned by the apps that they use. For businesses building apps on Nostr, sovereignty means that every app actually benefits by other apps being on the network. Because sovereignty is respected, users are retained for longer and independent apps thrive far longer on Nostr than on the legacy “black box” social networks.
Social apps thrive on Nostr
Nostr integration provides these benefits for every app :
- Unrestrained access for any app, to all public and private data “on Nostr”. No fees or licenses for harvesting user data from the network.
- Unburdened from liability, when collecting user data with any app. When sending “to Nostr”, end users retain custody of user data while apps never loose access.
- Unlimited free market of search engines and feed algos. Users and brands can create, use, and share any algos or custom feeds. Grow your audience on your own terms.
- Universal open network for all apps. Build any kind of app for any audience, on the same network as other apps for other audiences. Discover new trends from user data.
- Unregulated tech platform. Build your own app and use it as you wish. No gate keepers. No code review.
Sovereignty is good for business.
Regardless of the network size, a Nostr integrated app can grow its user base MUCH faster and with greater independence BECAUSE of the sovereignty respecting protocol. While end users may retain custody of their identities and data on the network, it’s the apps that determine which data is, or is not, sent to the network. Respect for sovereignty IS the killer feature that ONLY the Nostr protocol provides for apps and for end users.
Because Nostr is permissionless for any app to integrate :
- end users will always have a free market of apps choose from
- apps are free to integrate only as much as benefits their business model.
- apps gain access to more novel data as new apps bring new users to the network.
Because data on Nostr is managed by end users and available to all apps :
- User data looses exclusivity and the demand shifts toward novel insights and information derived from these data.
- Apps are freed from having to be “data pirates”, and can focus on establishing a trusted user base, providing valuable services to satisfied customers, informed by the abundance of user data.
- Apps are incentivized to offload data onto the network, establishing a new paradigm for interconnectivity, where independence is NOT at stake as the network grows.
- New markets spring up to support users with self custody of their data, driven by the reality that apps can have full access without assuming responsibility.
- The market for search and algo tools opens up for independent apps and end users to discover and interact freely with each other.
- The ad based “attention economy” slowly transforms to a value based consumer economy, where the end user is the customer rather than the product being sold.
Even while privacy is respected
Sometimes sovereignty is at odds with privacy, but Nostr allows all parties to win while both are protected.
- For end users sending sensetive data "to Nostr", privacy is assured by encrypting it with their own private keys and/or sending it to private (auth required) relays of their choosing.
- For apps handling private IP or business data, any traditional “black box” infrastructure can be used in the back end to manitain isolation from Nostr.
This means apps and end users remain in control of their own private data, without requiring “big social” as trust provider or data reseller. To access a user's private data, client apps (even search engines, running locally) only need explicit permission from the end user to retrieve or decrypt from Nostr relays. Public data, on the other hand, is freely available for any app or search engine to harvest from any Nostr relay. In either case, user data on the Nostr network is always accessible to client apps, without additional restrictions or fees.
Nostr is for every app.
Adding social to any app makes it a better app. Add reviews for products or services. Add commenting or direct messaging. Share or collaborate on content creation. Nostr integration is straightforward and incremental for any app.
Nostr doesn't define your app's business model ... Nostr 10X's it!
Here's how :
- Start with your own business and app design. Add Nosrr login.
- Discover what "kinds" of user data already exists "on Nostr" that your app can ingest and make use of.
- Decide which "kinds" of data would benefit your business, your users, and the network, if sent "to Nostr".
- Implement Nostr integration for data kinds and add webs of trust tools for recommendation and discovery.
- Verify your app is sovereignty respecting in how it handles private data and implements Nostr NIPs.
- Engage with existing users, and onboard new users from your app, to earn their trust and patronage over Nostr.
For more info and assistance, contact our team of Nostr integration experts.
-
 @ 502ab02a:a2860397
2025-06-06 01:15:24
@ 502ab02a:a2860397
2025-06-06 01:15:24ปิดท้าย week นี้ด้วยสงครามดีไหมครับ ถ้าอาหารเป็นสนามรบ สิทธิบัตรก็เปรียบเหมือนป้อมปราการ และการฟ้องร้องก็คือปืนใหญ่ยิงสวนกันกลางแดด…ใครที่เคยคิดว่าโลกของอาหารแห่งอนาคตจะสวยงามเพราะเปลี่ยนถั่วเป็นสเต๊ก สกัดกลิ่นเลือดจากพืช หรือหลอกลิ้นให้เชื่อว่า “อร่อยเหมือนเนื้อ” ก็คงต้องมานั่งทบทวนใหม่ว่า โลกใบนี้ไม่ได้ขับเคลื่อนด้วยความฝัน แต่ขับเคลื่อนด้วยเอกสาร 70 หน้าของทนายความ และหมายเรียกจากศาลกลางรัฐเดลาแวร์
Motif FoodWorks เข้ามาในวงการอาหารด้วยวิสัยทัศน์สุดเท่ คือจะสร้างโครงสร้าง-กลิ่น-รส ของโปรตีนอนาคตให้แบรนด์ plant-based ทั่วโลกใช้ได้โดยไม่ต้องเริ่มใหม่ตั้งแต่ศูนย์ เปรียบเหมือนเป็นเบื้องหลังของวงการ มีซอสลับคือ HEMAMI™ ที่สกัดกลิ่นเนื้อจากยีสต์ ผ่านวิธีการทางวิทยาศาสตร์สุดซับซ้อน ฟังแล้วดูดี แต่ปัญหาคือซอสลับของเขาดัน “คล้ายเกินไป” กับของ Impossible Foods ที่ใช้ heme protein เหมือนกัน
แล้วอะไรคือจุดเปราะบางที่ทำให้ Motif ต้องร่วง?
เฮียอยากให้ลองคิดแบบนี้ครับ สมมุติว่ามีร้านกาแฟใหม่ที่ตั้งใจจะขายกาแฟแนวใหม่ ใช้เมล็ดกาแฟหมักยีสต์กลิ่นกล้วยหอม รสชาตินุ่มลึก เป็นของตัวเอง เขาไม่ได้ก็อปสูตรใคร แต่ดันไปใช้กระบวนการคล้ายกับแบรนด์เจ้าตลาดที่เขียนจดสิทธิบัตรเอาไว้ก่อนแล้ว แค่คล้ายก็พอจะโดนลากขึ้นศาลได้ เพราะในโลกของสิทธิบัตร “ความใหม่” และ “ความไม่เหมือน” คือสิ่งศักดิ์สิทธิ์ แม้จะไม่ได้ก็อปตรง ๆ
Impossible Foods เห็นช่องนี้ชัด พวกเขายื่นฟ้องทันที โดยระบุว่า HEMAMI™ ของ Motif ละเมิดสิทธิบัตรเทคนิคการใช้ heme เพื่อสร้างรสชาติเหมือนเนื้อในผลิตภัณฑ์ plant-based ซึ่งเป็นหัวใจหลักที่ Impossible ใช้มัดใจตลาดมาหลายปี
ในเดือนมีนาคม 2022, Impossible Foods ก็ลุกขึ้นมาฟ้อง Motif FoodWorks ต่อศาลรัฐบาลกลางของสหรัฐฯ โดยอ้างว่า HEMAMI™ ละเมิดสิทธิบัตรของตนที่เกี่ยวข้องกับการใช้โปรตีน heme ในการสร้างรสชาติและกลิ่นที่คล้ายเนื้อจริงในผลิตภัณฑ์จากพืช จุดนี้ดูผิวเผินเหมือนแค่ “บริษัท A เหมือนของบริษัท B เลยโดนฟ้อง” แต่ความจริงซับซ้อนและลึกกว่านั้นมาก เพราะทั้งสองบริษัทต่างก็ใช้วิธีผลิตโปรตีน heme ที่คล้ายกันมาก นั่นคือการดัดแปลงพันธุกรรมจุลินทรีย์ให้ผลิตโปรตีนเฉพาะ แล้วหมักออกมาในถังขนาดใหญ่ แต่ต่างกันที่วัตถุดิบและดีไซน์โปรตีน
Impossible Foods ใช้ “soy leghemoglobin” ซึ่งเป็นโปรตีน heme จากรากถั่วเหลือง ส่วน Motif ใช้ “bovine myoglobin” ซึ่งเลียนแบบของวัวจริง ๆ โดยตรง ความคล้ายคือโปรตีนทั้งสองต่างก็ให้กลิ่นคาวแบบเนื้อเมื่อโดนความร้อน และสร้างสีแดงแบบ rare steak ได้เหมือนกัน ทั้งยังถูกหมักด้วยจุลินทรีย์ GMO แบบใกล้เคียงกันอีกด้วย แม้จะต่างสายพันธุ์ของโปรตีน แต่การฟ้องครั้งนี้ตั้งอยู่บนแนวคิดว่า “วิธีการใช้” โปรตีน heme ในอาหารจากพืชอาจเข้าข่ายละเมิดสิทธิบัตร
จากนั้นไม่กี่เดือน Motif ก็สวนกลับโดยการยื่นคำร้อง “Inter Partes Review” (IPR) กับสำนักงานสิทธิบัตรของสหรัฐฯ (USPTO) ผ่าน PTAB ซึ่งเป็นขั้นตอนที่ใช้เพื่อขอให้ตรวจสอบความถูกต้องของสิทธิบัตรที่กำลังมีปัญหา แนวคิดคือถ้าพิสูจน์ได้ว่าสิทธิบัตรของ Impossible นั้นไม่ใหม่จริง หรือมี prior art อยู่ก่อนแล้ว (เช่น งานวิจัยเก่า ๆ ที่ตีพิมพ์ก่อน) ก็จะทำให้สิทธิบัตรนั้นกลายเป็นโมฆะ
Motif ยื่นคำร้องโจมตีสิทธิบัตรถึง 7 ฉบับของ Impossible แบบกระหน่ำชุดใหญ่ ยิงทีเดียวหวังให้สั่นคลอนทั้งระบบ แต่ PTAB รับพิจารณาเพียงฉบับเดียว (หมายเลขสิทธิบัตร 10,933,018) และท้ายที่สุดในเดือนเมษายน 2023 ศาลตัดสินยกเลิกฉบับนั้นจริง โดยให้เหตุผลว่า “ไม่เป็นสิ่งประดิษฐ์ใหม่อย่างเพียงพอ” ซึ่งถือเป็นชัยชนะเล็ก ๆ ของ Motif และสร้างแรงกระเพื่อมในแวดวงวิทยาศาสตร์อาหารอยู่พอสมควร
แต่แม้จะมีชัยบางส่วน อีก 6 ฉบับที่เหลือ PTAB กลับไม่รับพิจารณา โดยบอกว่า “หลักฐานไม่ชัดเจนพอจะเข้าขั้นพิจารณาใหม่” นั่นทำให้ฝั่ง Impossible ยังถือสิทธิบัตรส่วนใหญ่ไว้อยู่เหมือนเดิม แล้วก็เริ่มกลับมาเร่งกระบวนการฟ้องร้องในศาลต่อ ซึ่งหมายความว่า Motif ยิ่งต้องใช้เงินมากขึ้นเรื่อย ๆ ในการสู้รบทั้งสองด้าน ทั้งในศาลและในระบบสิทธิบัตร
ชัยชนะเล็ก ๆ นี้กลายเป็นดาบสองคม เพราะในขณะที่ Motif ดีใจว่าล้มได้ 1 ฉบับ ตลาดกลับมองว่าพวกเขาสู้แบบดิ้นสุดตัว ซึ่งในมุมของนักลงทุน นั่นแปลว่า "ขาดเงินทุนหมุนเวียน" หรือ “มีแนวโน้มขาดทุนต่อเนื่อง” มากกว่าจะมองว่าเป็นฮีโร่สู้เพื่อความถูกต้อง
ระหว่างนี้ Motif ยังพยายาม “spin” ภาพลักษณ์ตัวเองในเชิงบวกอย่างหนัก พวกเขาเปิดตัวผลิตภัณฑ์ใหม่ชื่อ “Motif MoBeef™” และ “Motif MoChicken™” โดยใช้ HEMAMI™ ผสมอยู่ พร้อมโชว์ผลงานให้เชฟชื่อดังระดับ Michelin มาชิมและออกสื่อ โดยหวังว่าจะสร้างความเชื่อมั่นให้ตลาดว่า “ผลิตภัณฑ์เรายังไปต่อได้” และอาจดึงดีลใหม่หรือการลงทุนเพิ่มเข้ามาเพื่อบรรเทาภาระจากการฟ้องร้อง
และในขณะที่ Motif เดินหน้าเปิดตัวผลิตภัณฑ์ใหม่เพื่อแสดงพลังให้ตลาดเห็นว่า “เรายังไปต่อได้” ฝั่ง Impossible กลับเดินเกม PR อย่างเงียบ ๆ ด้วยการแจ้งเตือนสื่อและผู้ถือหุ้นว่า “Motif ยังใช้เทคโนโลยีละเมิดอยู่ต่อเนื่อง” พร้อมแนบเอกสารคำฟ้องเพิ่มในปี 2023 ซึ่งแปลความได้ว่า “ศึกยังไม่จบ อย่าเพิ่งส่งเงินให้คู่แข่งเรา” เพราะในเอกสารคำฟ้องของปี 2023 พวกเขาเสริมข้อกล่าวหาใหม่ว่าการที่ Motif ออกสื่อและใช้ HEMAMI™ ต่อไป “เป็นการจงใจละเมิด” และอาจเข้าข่ายการทำลายคุณค่าของแบรนด์ Impossible โดยตรง จุดนี้ยิ่งทำให้ Motif อยู่ในมุมที่เสี่ยงและลำบากมากขึ้น
การต่อสู้ของทั้งสองบริษัทจึงไม่ใช่แค่เรื่องใครเลียนแบบใคร แต่มันคือเกมยืดเวลา เผาเงิน ปั่นมูลค่า และวัดใจนักลงทุนว่าใครจะถอยก่อนกัน และสุดท้ายคนที่หมดลมหายใจก่อนก็คือ Motif แม้จะมีนักวิทยาศาสตร์เก่ง ๆ เทคโนโลยีล้ำ ๆ หรือวัตถุดิบดีแค่ไหน แต่เมื่อต้องมาสู้กับยักษ์ที่มีสิทธิบัตรในมือ บารมีในตลาด และชื่อเสียงติดหูผู้บริโภค…ก็ยากที่จะเอาชนะด้วยวิทยาศาสตร์เพียงอย่างเดียว
ศึกนี้จึงไม่ได้จบแค่ในศาล แต่มันลากไปถึงห้องประชุมนักลงทุน พาดหัวข่าวใน Business Insider และบอร์ด Reddit ที่คุยกันว่า “Motif จะไปไม่รอดหรือเปล่า” ซึ่งในยุคที่เงินทุนคือออกซิเจน การที่ภาพลักษณ์ของบริษัทเริ่มสั่นคลอน ก็เหมือนถังอากาศรั่วในห้องแล็บใต้ทะเล…ไม่นานนัก Motif ก็เริ่มลดจำนวนพนักงาน ลดเป้าการผลิต และสุดท้าย “ลดบทบาทตัวเองในตลาด”
หากดูเผิน ๆ หลายคนอาจคิดว่านี่คือเรื่องของสองบริษัทใหญ่ในโลก plant-based ที่ทะเลาะกันเอง แต่จริง ๆ แล้วนี่คือบทเรียนใหญ่ของ “วงการอาหารแห่งอนาคต” ที่กำลังเติบโตบนหลังคำว่า IP Intellectual Property ใครถือสิทธิบัตรก่อน คนนั้นตั้งกฎได้ ใครมาใหม่ ถ้าไม่จดให้ไว ก็อาจต้องจ่ายค่าต๋งตลอดชีวิต
และที่เจ็บปวดที่สุดคือบางทีของที่คุณคิดขึ้นมาเอง อาจไม่ใช่ของคุณอีกต่อไปแล้ว ถ้าคุณไม่มีเอกสารในมือ
นี่แหละครับ วงการที่ดูเหมือนจะขาย “นวัตกรรมอาหาร” แต่จริง ๆ แล้วขาย “สิทธิบัตรในกล่องข้าว” ใครจะอยู่ใครจะไป บางทีก็ไม่เกี่ยวกับว่า “ของอร่อยแค่ไหน” แต่เกี่ยวกับว่า “ใครมีทนายเก่งกว่า”
และในขณะที่สองยักษ์ใหญ่ยิงกันด้วยเอกสารละเมิดสิทธิ์ เหยื่อเงียบ ๆ อย่างเกษตรกรรายย่อยที่ยังอยากปลูกผักจริง เลี้ยงวัวจริง หรือแม้แต่ผู้บริโภคที่แค่อยากรู้ว่า “กินอะไรแล้วร่างกายจะดีขึ้น” กลับวนเวียนในทางอยู่ในโลกที่อาหารทุกคำถูกควบคุมโดยทุน จดหมายเรียกจากศาล และวัตถุดิบสังเคราะห์ที่มีรหัสมากกว่าชื่อจริง
สงครามสิทธิบัตรเหล่านี้ไม่เคยมีพื้นที่ให้ชาวไร่ หรือผู้บริโภคธรรมดาเข้าไปมีเสียงเลยสักนิด เพราะมันคือการต่อสู้ระหว่างนักล่าที่ฟาดฟันกันบนยอดห่วงโซ่อาหาร แต่เบื้องล่างของพีระมิด กลับมีแต่เหยื่อที่ถูกเลี้ยงให้งุนงง อยู่กับของปลอม และเชื่อว่า “นี่แหละคืออนาคตของอาหาร”
แล้วใครจะบอกเราว่า...ทางรอดคืออะไร?
คำตอบอาจอยู่ไม่ไกล แค่เราต้องกลับมาถามคำถามง่าย ๆ ที่ใครก็ลืมไปว่า “จริง ๆ แล้ว เราต้องการอาหารแบบไหนกันแน่” อาหารที่กินแล้วแข็งแรง หรืออาหารที่บริษัทแข็งแรง?
เพราะตราบใดที่เรายังปล่อยให้กล่องข้าวอยู่ในมือคนจดสิทธิบัตร เราอาจไม่มีวันได้กลับไปจับจอบเอง ปลูกเอง กินเอง แบบที่มนุษย์เคยเป็นมาก่อนโลกจะกลายเป็นห้องทดลองขนาดยักษ์
ศึกระหว่างผู้ล่ายังรุนแรงขนาดนี้ แล้วศึกระหว่างผู้ล่ากับเหยื่อ จะเหลืออะไรครับ
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 374ee93a:36623347
2025-06-05 22:42:00
@ 374ee93a:36623347
2025-06-05 22:42:00Chef's notes
Start your day the self sovereign way
Details
- ⏲️ Prep time: 10 mins
- 🍳 Cook time: 15 mins
- 🍽️ Servings: 4
Ingredients
- 1lb Jar Bottled Rhubarb https://jimblesjumble.netlify.app/item/a0c35618722834ac714d0a47058a2adc76ee7485a6b74f5da5f9eb2d3fb5d879
- 1pt Homemade Custard (3/4pt cream, 3 large eggs, 100g honey, 1/2 tbspn vanilla extract)
- 4 Handfuls Granola
- 1 Node https://plebeian.market/products/huxley@nostrplebs.com/start-9-node-y22zfjp8x6
Directions
- Whisk together the cream, eggs, honey and vanilla
- Chill overnight or serve warm with 1/4 jar of stewed rhubarb and a large handful of granola per person
- Consolidate some UTXOs on your node
- Have a Good Morning
-
 @ dfa02707:41ca50e3
2025-06-06 02:01:40
@ dfa02707:41ca50e3
2025-06-06 02:01:40
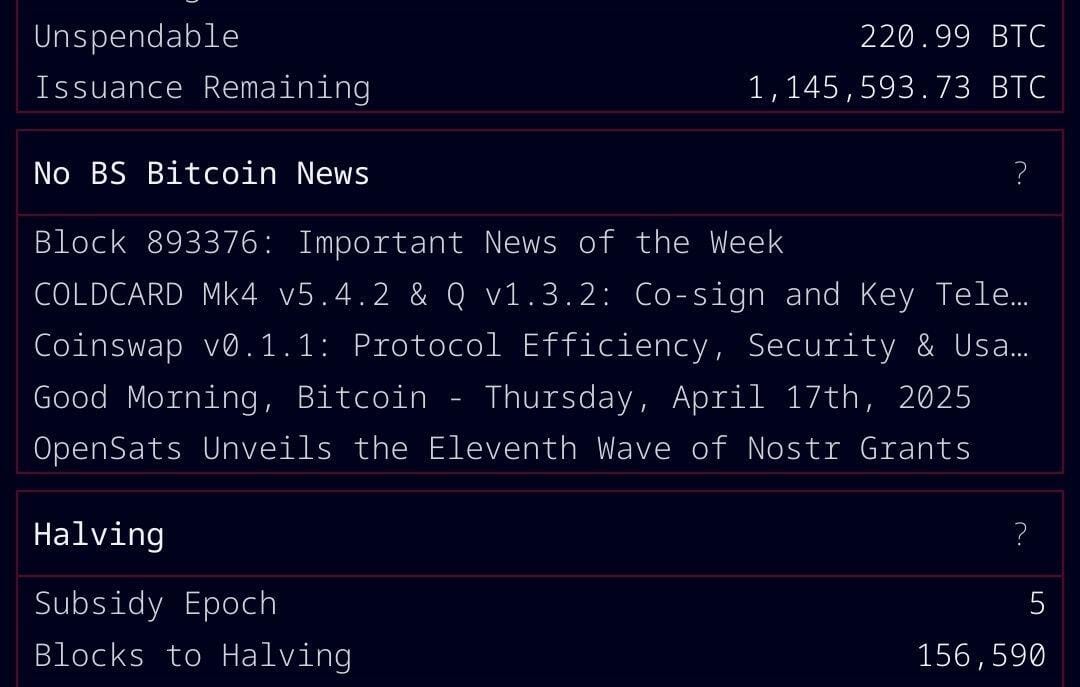
Good morning (good night?)! The No Bullshit Bitcoin news feed is now available on Moody's Dashboard! A huge shoutout to sir Clark Moody for integrating our feed.
Headlines
- Spiral welcomes Ben Carman. The developer will work on the LDK server and a new SDK designed to simplify the onboarding process for new self-custodial Bitcoin users.
- The Bitcoin Dev Kit Foundation announced new corporate members for 2025, including AnchorWatch, CleanSpark, and Proton Foundation. The annual dues from these corporate members fund the small team of open-source developers responsible for maintaining the core BDK libraries and related free and open-source software (FOSS) projects.
- Strategy increases Bitcoin holdings to 538,200 BTC. In the latest purchase, the company has spent more than $555M to buy 6,556 coins through proceeds of two at-the-market stock offering programs.
- Spar supermarket experiments with Bitcoin payments in Zug, Switzerland. The store has introduced a new payment method powered by the Lightning Network. The implementation was facilitated by DFX Swiss, a service that supports seamless conversions between bitcoin and legacy currencies.
- The Bank for International Settlements (BIS) wants to contain 'crypto' risks. A report titled "Cryptocurrencies and Decentralised Finance: Functions and Financial Stability Implications" calls for expanding research into "how new forms of central bank money, capital controls, and taxation policies can counter the risks of widespread crypto adoption while still fostering technological innovation."
- "Global Implications of Scam Centres, Underground Banking, and Illicit Online Marketplaces in Southeast Asia." According to the United Nations Office on Drugs and Crime (UNODC) report, criminal organizations from East and Southeast Asia are swiftly extending their global reach. These groups are moving beyond traditional scams and trafficking, creating sophisticated online networks that include unlicensed cryptocurrency exchanges, encrypted communication platforms, and stablecoins, fueling a massive fraud economy on an industrial scale.
- Slovenia is considering a 25% capital gains tax on Bitcoin profits for individuals. The Ministry of Finance has proposed legislation to impose this tax on gains from cryptocurrency transactions, though exchanging one cryptocurrency for another would remain exempt. At present, individual 'crypto' traders in Slovenia are not taxed.
- Circle, BitGo, Coinbase, and Paxos plan to apply for U.S. bank charters or licenses. According to a report in The Wall Street Journal, major crypto companies are planning to apply for U.S. bank charters or licenses. These firms are pursuing limited licenses that would permit them to issue stablecoins, as the U.S. Congress deliberates on legislation mandating licensing for stablecoin issuers.
"Established banks, like Bank of America, are hoping to amend the current drafts of [stablecoin] legislation in such a way that nonbanks are more heavily restricted from issuing stablecoins," people familiar with the matter told The Block.
- Charles Schwab to launch spot Bitcoin trading by 2026. The financial investment firm, managing over $10 trillion in assets, has revealed plans to introduce spot Bitcoin trading for its clients within the next year.
Use the tools
- Bitcoin Safe v1.2.3 expands QR SignMessage compatibility for all QR-UR-compatible hardware signers (SpecterDIY, KeyStone, Passport, Jade; already supported COLDCARD Q). It also adds the ability to import wallets via QR, ensuring compatibility with Keystone's latest firmware (2.0.6), alongside other improvements.
- Minibits v0.2.2-beta, an ecash wallet for Android devices, packages many changes to align the project with the planned iOS app release. New features and improvements include the ability to lock ecash to a receiver's pubkey, faster confirmations of ecash minting and payments thanks to WebSockets, UI-related fixes, and more.
- Zeus v0.11.0-alpha1 introduces Cashu wallets tied to embedded LND wallets. Navigate to Settings > Ecash to enable it. Other wallet types can still sweep funds from Cashu tokens. Zeus Pay now supports Cashu address types in Zaplocker, Cashu, and NWC modes.
- LNDg v1.10.0, an advanced web interface designed for analyzing Lightning Network Daemon (LND) data and automating node management tasks, introduces performance improvements, adds a new metrics page for unprofitable and stuck channels, and displays warnings for batch openings. The Profit and Loss Chart has been updated to include on-chain costs. Advanced settings have been added for users who would like their channel database size to be read remotely (the default remains local). Additionally, the AutoFees tool now uses aggregated pubkey metrics for multiple channels with the same peer.
- Nunchuk Desktop v1.9.45 release brings the latest bug fixes and improvements.
- Blockstream Green iOS v4.1.8 has renamed L-BTC to LBTC, and improves translations of notifications, login time, and background payments.
- Blockstream Green Android v4.1.8 has added language preference in App Settings and enables an Android data backup option for disaster recovery. Additionally, it fixes issues with Jade entry point PIN timeout and Trezor passphrase input.
- Torq v2.2.2, an advanced Lightning node management software designed to handle large nodes with over 1000 channels, fixes bugs that caused channel balance to not be updated in some cases and channel "peer total local balance" not getting updated.
- Stack Wallet v2.1.12, a multicoin wallet by Cypher Stack, fixes an issue with Xelis introduced in the latest release for Windows.
- ESP-Miner-NerdQAxePlus v1.0.29.1, a forked version from the NerdAxe miner that was modified for use on the NerdQAxe+, is now available.
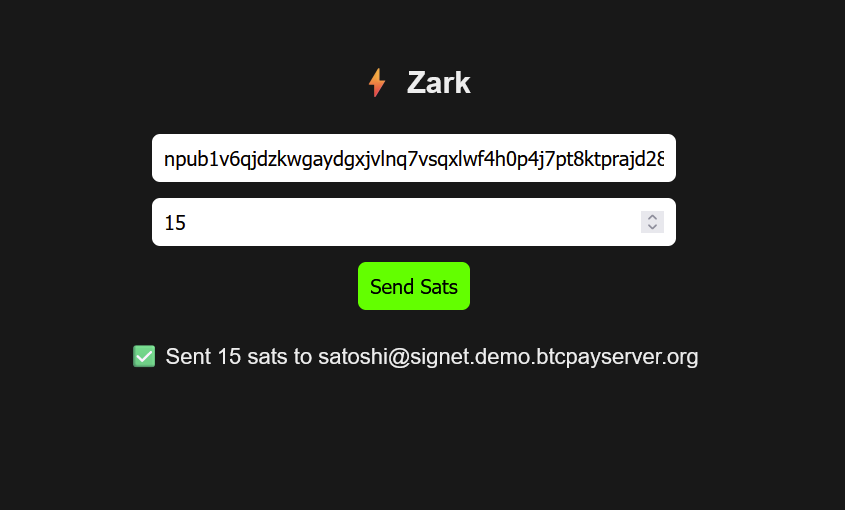
- Zark enables sending sats to an npub using Bark.
- Erk is a novel variation of the Ark protocol that completely removes the need for user interactivity in rounds, addressing one of Ark's key limitations: the requirement for users to come online before their VTXOs expire.
- Aegis v0.1.1 is now available. It is a Nostr event signer app for iOS devices.
- Nostash is a NIP-07 Nostr signing extension for Safari. It is a fork of Nostore and is maintained by Terry Yiu. Available on iOS TestFlight.
- Amber v3.2.8, a Nostr event signer for Android, delivers the latest fixes and improvements.
- Nostur v1.20.0, a Nostr client for iOS, adds
-
 @ 2cde0e02:180a96b9
2025-06-05 21:45:00
@ 2cde0e02:180a96b9
2025-06-05 21:45:00日本の姫
https://stacker.news/items/998335
-
 @ 90c656ff:9383fd4e
2025-06-05 12:27:43
@ 90c656ff:9383fd4e
2025-06-05 12:27:43When people talk about Bitcoin, it’s often described as a digital currency or a “speculative investment.” However, one of Bitcoin’s most fundamental and least understood roles is its function as a settlement network. To understand this, it’s worth comparing it with traditional settlement systems like SWIFT and exploring how Bitcoin offers a foundational layer for global value transfer decentralized and censorship-resistant.
First, let’s explain the difference between liquidity and settlement:
-
Liquidity refers to the ease with which an asset can be converted into “money” without losing value.
-
Settlement is the process of completing a transaction (actual transfer of value between parties).
SWIFT: The communication layer of the traditional financial system
The SWIFT system (Society for Worldwide Interbank Financial Telecommunication) is a network for communication between banks. It doesn’t move money directly but sends standardized messages that instruct financial institutions to perform transfers. The process involves multiple intermediaries, is costly, slow (can take days), and depends on trust between parties and local regulations.
Unlike SWIFT, Bitcoin is a self-sufficient network that enables the direct settlement of value between two parties, without the need for intermediaries. With each block mined, transactions are validated and recorded immutably in a global, transparent, and secure database: the timechain or "blockchain".
01 - Final settlement: Once a transaction is confirmed by a sufficient number of blocks, it is considered final and irreversible.
02 - Censorship resistance: There is no central entity that can block or reverse a valid transaction.
03 - Global availability: The network is accessible 24/7 anywhere in the world with internet access.
Just as gold once served as the foundation of monetary systems, Bitcoin is establishing itself as a base layer of digital value. This layer can support others, such as:
01 - The Lightning Network, which enables near-instant transactions with extremely low fees;
02 - Tokenized financial services, which can use Bitcoin as collateral or for inter-institutional settlement.
By functioning as a public and neutral settlement network, Bitcoin offers an alternative to the traditional system, which is fragmented, closed, and reliant on trust between institutions.
In summary, more than just a speculative asset, Bitcoin is emerging as a global financial infrastructure. As a settlement network, it removes intermediaries, reduces costs, increases security, and democratizes access to value transfer. In an increasingly interconnected and digital world, understanding Bitcoin’s role as a base layer may be key to understanding the future of money.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
-
 @ f85b9c2c:d190bcff
2025-06-06 01:02:16
@ f85b9c2c:d190bcff
2025-06-06 01:02:16
Cristiano Ronaldo stands out as a recognized and accomplished football player on a scale. His inspiring journey, from beginnings in Portugal to attaining superstar status serves as an inspiration, to individuals.
Ronaldo’s prodigious talent was evident from a young age. His coach at Sporting CP famously said “He was skinny when he arrived here but with tremendous skill”. Through hard work and dedication, Ronaldo honed his skills
Some Work Ethic and Ambition that Fuelled his success .A key factor in Ronaldo’s success story is his incredible work ethic and winning mentality. He is renowned for his strict training regimen, nutrition plan, and diligent recovery routines. Ronaldo’s dedication to self-improvement paved the way for his success. .Throughout his career, Ronaldo has shown insatiable hunger and ambition to be the best. His drive to succeed and break records is unmatched. Even in the twilight of his career, Ronaldo’s success story continues as he plies his trade in Italy with Juventus.
Lessons from Ronaldo’s Success Story 1. Dedication and hard work are essential Ronaldo showed how training relentlessly can make dreams come true. 2. Believe in your talent Ronaldo had the confidence and work ethic to fulfill his potential. 3. Handle pressure with grace Ronaldo embraced the spotlight and thrived under pressure. 4. Be ambitious and hungry Ronaldo set new benchmarks by constantly raising the bar. 5. Lead by example Ronaldo inspires teammates with his exemplary attitude. 6. Learn and improve Even at the top Ronaldo keeps evolving and adding new skills. 7. Give back Ronaldo uses his global fame and fortune for charity work.
Sum Up Cristiano Ronaldo's remarkable journey showcases the heights that can be reached through a combination of talent and relentless effort. His success serves as an inspiration for anyone with dreams and the determination to make them a reality.
-
 @ f85b9c2c:d190bcff
2025-06-06 00:24:22
@ f85b9c2c:d190bcff
2025-06-06 00:24:22
Inflation is one of the most significant factors affecting personal wealth and the economy yet it goes unnoticed until its effects become unavoidable. As the cost of goods and services rises, your purchasing power decreases, and this makes long-term financial planning more challenging.
What is inflation? Inflation is the general increase in prices of goods and the reduction of the purchasing power of money. It is commonly measured by : 1.Consumer Price Index (CPI)
2.Core Inflation
3.Producer Price Index (PPI)
Inflation occurs due to various factors, including increased demand and supply chain disruptions
Why is Inflation Important? Inflation is crucial because it affects the cost of living, purchasing power, and the economy as a whole. As prices rise money loses value making it harder for consumers to afford essentials if wages don’t keep up. It also influences interest rates as central banks ,adjust policies to control inflation, borrowing, savings, and investments.
How Inflation Affects Personal Wealth 1. Erosion of Purchasing Power As prices rise, the same amount of money used to buy more before now buys fewer goods and services. 2. Impact on Savings Your money sitting in savings accounts with little or no interest rates loses value over time. If the inflation rate exceeds the interest or profit earned on your savings, then it becomes affected 3. Effects on Investments Their impact is the most because inflation reduces the real value of future payments. 4.Wages & Employment Some businesses may cut costs by reducing roles in a department or reducing pay to keep the team members.
Everyone is affected by inflation.
How Do You Protect Your Wealth from Inflation? 1.Invest in Inflation-Protected Assets Stocks and real estate investments offer long-term growth potential.They give you ownership of a product, which you can use, resell or repackage as you please. 2.Alternative Investments If you have the stomach, commodities, cryptocurrency, and other non-traditional assets may provide inflation releaved. 3. Increase Income Streams Side hustles, passive income, and career advancements can help offset inflation’s impact. 4.Reduce Debt Nigerians are aware of Credit Houses pretending as Loan Sharks chasing debtors around with ridiculous messages of loved ones. In a period of inflation, those loans feel like a double punishment because of ridiculous interest rates and overwhelmed inflation. Whatever you can do to reduce your debt during this period will be life-changing. Also, non-interest debts should always be considered before going down a slippery slope.
Summary Nigeria — A Few Word One thing is clear — inflation persists in almost every corridor of the economy. Inflation is an inevitable part of economic cycles, but understanding its impact allows you to take proactive steps in protecting your wealth. But I believe you can maintain financial stability by following some of the steps above.
Be proactive!
-
 @ ac8bb9b0:70278acc
2025-06-05 18:12:29
@ ac8bb9b0:70278acc
2025-06-05 18:12:29Details
- ⏲️ Prep time: 15 min
- 🍳 Cook time: 20 min
- 🍽️ Servings: 12
Ingredients
- 1 and 1/2 cups (345g) mashed bananas (about 4 medium or 3 large ripe bananas)
- 1/3 cup (113g) honey
- 1 large egg
- 1/4 cup (56g) coconut oil, melted
- 1 teaspoon pure vanilla extract
- 1 cup (130g) whole wheat flour
- 1/2 cup (41g) natural unsweetened cocoa powder
- 1 teaspoon baking powder
- 1 teaspoon baking soda
- 1/2 teaspoon salt
- 1 cup (180g) semi-sweet or dark chocolate chips
Directions
- Preheat oven to 425°F (218°C). Spray a 12-count muffin pan with nonstick spray or line with cupcake liners. Set aside.
- In a medium bowl, mash the bananas up using a fork.* Try to mash up any large lumps. Once mashed, whisk in the honey, egg, coconut oil, and vanilla extract until combined. Set aside.
- In a large bowl, whisk the flour, cocoa powder, baking powder, baking soda, and salt together. Pour the wet ingredients into the dry ingredients and whisk until everything is combined. Fold in the chocolate chips, reserving some for the tops of the warm muffins.
- Spoon the batter evenly into each cup or liner, filling each all the way to the top.
- Bake for 5 minutes at 425°F (218°C); then, keeping the muffins in the oven, reduce heat to 350°F (177°C) and continue baking for another 15–17 minutes or until a toothpick inserted in the center comes out clean. The total time these muffins take in the oven is about 20–21 minutes, give or take. (For mini muffins, bake 11–13 minutes at 350°F (177°C) the whole time.)
- Press any remaining chocolate chips into the tops of the warm muffins. Allow the muffins to cool for 5 minutes in the muffin pan, and then transfer to a wire rack to continue cooling, or enjoy warm.
- Muffins stay fresh covered at room temperature for a few days, then transfer to the refrigerator for up to 1 week.
-
 @ 42a071ab:3391e086
2025-06-05 20:06:56
@ 42a071ab:3391e086
2025-06-05 20:06:5688VIN đã từng bước khẳng định vị thế của mình trên thị trường bằng cách không ngừng đầu tư vào chất lượng dịch vụ và sự hài lòng của người dùng. Khác với những nền tảng thông thường, 88VIN chú trọng vào việc xây dựng một hệ sinh thái vận hành bài bản, nơi mọi quy trình đều được chuẩn hóa và tối ưu để đem lại hiệu suất cao nhất. Từ bước đăng ký tài khoản, xác thực thông tin, cho đến nạp – rút tiền và hỗ trợ khách hàng, tất cả đều được thiết kế một cách khoa học, rõ ràng và minh bạch. Sự tiện lợi trong thao tác và tính linh hoạt trong hệ thống đã giúp 88VIN tạo được sự tin tưởng vững chắc từ phía người dùng. Hệ thống hoạt động ổn định, tốc độ xử lý nhanh chóng, cùng đội ngũ chăm sóc khách hàng chuyên nghiệp, nhiệt tình 24/7 chính là những yếu tố làm nên thành công bền vững của 88VIN. Không chỉ vậy, nền tảng còn tích hợp công nghệ bảo mật hiện đại, bảo vệ an toàn tuyệt đối cho mọi thông tin và giao dịch cá nhân, giúp người dùng yên tâm tuyệt đối khi sử dụng.
Bên cạnh sự hoàn hảo về hệ thống, 88VIN còn gây ấn tượng bởi chính sách hỗ trợ người dùng rõ ràng, minh bạch và đầy tính nhân văn. Thay vì chỉ chú trọng vào mặt kỹ thuật, 88VIN hiểu rằng yếu tố con người mới là cốt lõi cho sự phát triển lâu dài. Chính vì vậy, đội ngũ chăm sóc khách hàng tại đây không chỉ được đào tạo bài bản mà còn luôn sẵn sàng lắng nghe, thấu hiểu và đồng hành cùng người dùng trong mọi tình huống. Mỗi phản hồi, dù là nhỏ nhất, đều được ghi nhận nghiêm túc để làm cơ sở nâng cấp chất lượng dịch vụ. Điều này giúp tạo nên một cộng đồng sử dụng 88VIN văn minh, gắn bó và ngày càng phát triển. Đồng thời, việc tối ưu hóa trải nghiệm người dùng được thể hiện qua từng chi tiết nhỏ, từ giao diện hiển thị, bố cục chức năng đến tốc độ phản hồi trên mọi thiết bị. Chính nhờ sự chăm chút tỉ mỉ đó, 88VIN không chỉ đáp ứng nhu cầu trước mắt mà còn luôn sẵn sàng cải tiến để bắt kịp xu hướng trong tương lai.
88VIN không đơn thuần là một nền tảng cung cấp dịch vụ chất lượng cao mà còn là biểu tượng của sự cam kết lâu dài đối với người dùng. Mỗi thành viên khi đến với 88VIN đều được đảm bảo quyền lợi rõ ràng, được đồng hành trong môi trường minh bạch và công bằng. Sự khác biệt của 88VIN chính là khả năng duy trì sự ổn định trong khi vẫn không ngừng đổi mới và hoàn thiện. Những giá trị mà 88VIN theo đuổi không chỉ nằm ở hiệu quả vận hành mà còn là sự tận tâm trong từng trải nghiệm của người dùng. Đây là yếu tố quyết định giúp nền tảng ngày càng chiếm được lòng tin và sự lựa chọn của cộng đồng. Trong thời đại mà sự cạnh tranh ngày càng khốc liệt, việc giữ vững đạo đức kinh doanh, coi trọng người dùng và luôn đặt chất lượng lên hàng đầu chính là con đường bền vững mà 88VIN đang theo đuổi. Nhờ vậy, 88VIN ngày càng khẳng định vị trí vững chắc, trở thành điểm đến tin cậy cho những ai tìm kiếm một nền tảng chuyên nghiệp, ổn định và thực sự vì lợi ích của người dùng.
-
 @ da8b7de1:c0164aee
2025-06-05 17:39:41
@ da8b7de1:c0164aee
2025-06-05 17:39:41| Régió/Ország | Fő esemény/politika | Forrás | |------------------|--------------------------------------------------------------------------------------------------|-------------| | Egyesült Államok | Végrehajtási rendeletek a nukleáris termelés négyszeresére növeléséről; a nem létfontosságú K+F költségvetésének csökkentése; SMR és mikroreaktor kezdeményezések | world-nuclear-news, nucnet, aoshearman, ans | | Kanada | Engedélyezés új BWRX-300 SMR reaktor építésére Darlingtonban | world-nuclear-news, ans | | Európa | EU tervek az orosz nukleáris importok korlátozására; Westinghouse–Bulgária beszállítói megállapodások | nucnet, world-nuclear-news | | Globális/Világbank | A nukleáris finanszírozási tilalom esetleges feloldása a fejlődő országok számára | globalissues | | Egyesült Királyság| Új kiberbiztonsági jogszabályok a nukleáris szektorban | aoshearman | | Katonaság/Védelem| A védelmi minisztérium cégeket választott ki mikroreaktorok telepítésére | ans |
Források:
world-nuclear-news
nucnet
aoshearman
globalissues
ans -
 @ 20e7c953:3b8bcb21
2025-06-05 10:32:40
@ 20e7c953:3b8bcb21
2025-06-05 10:32:4021… That number means something. A reminder that limits create value - both in Bitcoin and in life.
Every June 21st, skaters around the world remind us that freedom is something you make yourself - one push at a time only constrained by your own limitations.
This year in Vientiane, we’re proud to support one of the few real skate spots in Laos. A place built and held together by skaters for skaters.
Expect around 50 locals - from young kids to older heads - showing up not just to skate, but to hold space for each other. No ego, no filters, just boards, fun and respect.
Bircoiners have lots to learn from these communities on this regard. Go skate and you'll find out.
SnF
Laostr
Skateboardingisfun
Skate4Fun
-
 @ cae03c48:2a7d6671
2025-06-05 20:01:27
@ cae03c48:2a7d6671
2025-06-05 20:01:27Bitcoin Magazine

Moscow Exchange Launches Bitcoin Futures For Qualified InvestorsThe Moscow Exchange, Russia’s largest exchange group, announced the launch of Bitcoin futures contracts on June 4th, 2025. The new derivatives will allow qualified investors in Russia to gain exposure to bitcoin prices without directly owning it.
The bitcoin futures contracts are cash-settled in Russian rubles and will be tied to the iShares Bitcoin Trust ETF (IBIT) that trades on U.S. exchanges. The IBIT ETF tracks the price of bitcoin, with each share representing 0.00068 bitcoin.
BREAKING:
 Russia’s largest exchange, Moscow Exchange launches #Bitcoin futures trading for qualified investors. pic.twitter.com/J9htJUWpLw
Russia’s largest exchange, Moscow Exchange launches #Bitcoin futures trading for qualified investors. pic.twitter.com/J9htJUWpLw— Bitcoin Magazine (@BitcoinMagazine) June 4, 2025
Trading for the new bitcoin futures kicked off on Wednesday, with the first contracts expiring in September 2025. Each futures contract will be denominated in U.S. dollars per bitcoin but settled in rubles.
The launch of bitcoin futures on the Moscow Exchange comes after increased interest in Bitcoin exposure from Russian financial institutions. In May, Russia’s central bank formally permitted the offering of crypto-linked securities and derivatives to qualified investors. Prior to this, direct investment in Bitcoin was discouraged.
Sberbank, Russia’s largest bank, also announced plans to unveil its own bitcoin futures product in addition to the Moscow Exchange’s offering. The bank is launching exchange-traded notes that track Bitcoin’s price without direct ownership.
Bitcoin futures and other crypto-derivatives have seen surging interest recently as the Bitcoin and crypto industry matures. The move comes as an increasing number of countries have started adding Bitcoin to their reserves.
As Bitcoin adoption increases, investors and financial institutions are seeking more routes to gain exposure to Bitcoin. The launch of futures on the Moscow Exchange provides regulated bitcoin exposure to qualified Russian investors. But direct ownership of “physical” bitcoin remains off limits for most in Russia’s traditional finance sector.
This post Moscow Exchange Launches Bitcoin Futures For Qualified Investors first appeared on Bitcoin Magazine and is written by Vivek Sen.
-
 @ b1ddb4d7:471244e7
2025-06-05 10:00:43
@ b1ddb4d7:471244e7
2025-06-05 10:00:43Starting January 1, 2026, the United Kingdom will impose some of the world’s most stringent reporting requirements on cryptocurrency firms.
All platforms operating in or serving UK customers-domestic and foreign alike-must collect and disclose extensive personal and transactional data for every user, including individuals, companies, trusts, and charities.
This regulatory drive marks the UK’s formal adoption of the OECD’s Crypto-Asset Reporting Framework (CARF), a global initiative designed to bring crypto oversight in line with traditional banking and to curb tax evasion in the rapidly expanding digital asset sector.
What Will Be Reported?
Crypto firms must gather and submit the following for each transaction:
- User’s full legal name, home address, and taxpayer identification number
- Detailed data on every trade or transfer: type of cryptocurrency, amount, and nature of the transaction
- Identifying information for corporate, trust, and charitable clients
The obligation extends to all digital asset activities, including crypto-to-crypto and crypto-to-fiat trades, and applies to both UK residents and non-residents using UK-based platforms. The first annual reports covering 2026 activity are due by May 31, 2027.
Enforcement and Penalties
Non-compliance will carry stiff financial penalties, with fines of up to £300 per user account for inaccurate or missing data-a potentially enormous liability for large exchanges. The UK government has urged crypto firms to begin collecting this information immediately to ensure operational readiness.
Regulatory Context and Market Impact
This move is part of a broader UK strategy to position itself as a global fintech hub while clamping down on fraud and illicit finance. UK Chancellor Rachel Reeves has championed these measures, stating, “Britain is open for business – but closed to fraud, abuse, and instability”. The regulatory expansion comes amid a surge in crypto adoption: the UK’s Financial Conduct Authority reported that 12% of UK adults owned crypto in 2024, up from just 4% in 2021.
Enormous Risks for Consumers: Lessons from the Coinbase Data Breach
While the new framework aims to enhance transparency and protect consumers, it also dramatically increases the volume of sensitive personal data held by crypto firms-raising the stakes for cybersecurity.
The risks are underscored by the recent high-profile breach at Coinbase, one of the world’s largest exchanges.
In May 2025, Coinbase disclosed that cybercriminals, aided by bribed offshore contractors, accessed and exfiltrated customer data including names, addresses, government IDs, and partial bank details.
The attackers then used this information for sophisticated phishing campaigns, successfully deceiving some customers into surrendering account credentials and funds.
“While private encryption keys remained secure, sufficient customer information was exposed to enable sophisticated phishing attacks by criminals posing as Coinbase personnel.”
Coinbase now faces up to $400 million in compensation costs and has pledged to reimburse affected users, but the incident highlights the systemic vulnerability created when large troves of personal data are centralized-even if passwords and private keys are not directly compromised. The breach also triggered a notable drop in Coinbase’s share price and prompted a $20 million bounty for information leading to the attackers’ capture.
The Bottom Line
The UK’s forthcoming crypto reporting regime represents a landmark in financial regulation, promising greater transparency and tax compliance. However, as the Coinbase episode demonstrates, the aggregation of sensitive user data at scale poses a significant cybersecurity risk.
As regulators push for more oversight, the challenge will be ensuring that consumer protection does not become a double-edged sword-exposing users to new threats even as it seeks to shield them from old ones.
-
 @ 2f5de000:2f9bcef1
2025-06-05 17:33:37
@ 2f5de000:2f9bcef1
2025-06-05 17:33:37I've wanted to write this piece for months. Not because I have anything against Jack Mallers personally - quite the opposite. But because I've watched a pattern emerge in Bitcoin that mirrors one of the most chilling dynamics in Atlas Shrugged: the systematic destruction of our most productive builders by the very people who should be celebrating them.
We are the looters. And Jack might just be our Hank Rearden.
The Underdog's Dilemma
There's a cruel irony in how we treat success in Bitcoin. We champion the underdog, root for the builder in the garage, celebrate the cypherpunk taking on the establishment. But the moment that underdog succeeds - the moment they scale, grow, and inevitably have to navigate the messy realities of the existing system - we turn on them with the ferocity of the same establishment we claim to oppose.\ \ Jack began building Zap (which evolved into Strike) from his parents home in Chicago. Strike has grown into one of the most seamless fiat-to-bitcoin on-ramps for everyday users. No complexity, just pure utility. From day one, he's operated at a level of transparency that would make most CEO's uncomfortable. He's been building in public, taking feedback, admitting mistakes, and iterating - sometimes within hours of criticism.
The Rearden Parallel
In Atlas Shrugged, Hank Rearden creates Rearden Metal - a revolutionary alloy that's stronger, lighter, and more efficient than anything that came before. Instead of celebration, he faces endless scrutiny, regulation, and demands to prove is worthiness. The people who benefit from his innovation spend their time questioning his motives, dissecting his business practices, and demanding he justify his success.
Sound familiar?
Jack comes from a finance background - his father and grandfather were in the industry. This isn't a liability; it's an asset. He understands the beast we're fighting. He's been a Bitcoiner since 2013 with a spotless track record in a space littered with exit scams and broken promises. His values align with proof of work, individualism, and the radical idea that bitcoin is for everyone.
Yet when he helps launch 21 Capital, we don't see innovation - we see betrayal. When he navigates regulatory requirements to build products that can actually reach mainstream adoption, we don't see pragmatism - we see capitulation.
The Scarred Perspective
Our skepticism isn't entirely unfounded. We've been burned before. Mt. Gox, FTX, Three Arrows Capital, Celcius, Terra/ LUNA, BlockFi, Bitconnect, Voyager, QuadrigaCX - the graveyard of Bitcoin is littered with the corpses of trusted institutions. We've learned, painfully, that trust must be earned and verified.
But somewhere along the way, our healthy skepticism has metastasized into destructive paranoia. We've become so focused on protecting ourselves from the next SBF that we're attacking the people building the future we claim to want.
I'm guilty of this myself. I've made scathing attacks on my Nostr feed, comparing Jack to SBF, scrutinising contract clauses about re-hypothecation, and questioning his every move privately. I was viewing his actions through the lens of collective trauma rather than the reality of his long track record.
The Looters Paradox
Here's the uncomfortable truth: we're not just passive observers in this drama. We're active participants. We're the looters.
In Atlas Shrugged, the looters don't necessarily steal directly. They steal time, energy, and focus. They create bureaucracy, demnd endless justification, and burden the productive with the weight of constant explanation. They don't build competing products - they just tear down what others have built.
Everytime we demand Jack explain his business model for the hundredth time, we're stealing his time. Every time we scrutinize his partnerships without offering alternatives, we're creating bureaucracy . Everytime we attack his character rather than his arguments, we're furthering the system we claim to oppose.
The free market will create products whether we like them or not. People will build services that use bitcoin as collateral, create lending products, and navigate regulatory frameworks. The question isn't whether these products will exist - it's whether they'll be built by people who share our values or by those who don't.
The Atlantis Risk
The producers eventually withdraw from society in Atlas Shrugged, retreating to Galt's Gulch (Atlantis) and leaving the looters to face the consequences of their destructive behaviour. The economy collapses because the people who actually build things decided it wasn't worth the hassle anymore.
We're walking dangerously close to this precipice in Bitcoin. We're creating an environment where our most capable builders might just decide it's not worth it. Where the hassle of dealing with our constant scrutiny and bad-faith attacks outweighs the mission of building the future.
Jack has been more patient with our criticism than we deserve. He's addressed concerns publicly, changed the course when necessary, and continued building despite the noise. But patience has limits. At some point, even the most mission-driven builders will ask themselves: "Why am I doing this?"
The Path Forward
I don't know enough about finance to fully understand everything Jack is building with 21 Capital. Neither do most of his critics. But I know enough about Bitcoin to recognise someone who's been fighting the good fight for over a decade.
This doesn't mean we should trust blindly. It doesn't mean we should stop asking questions or demanding transparency. But it does mean we should approach our builders with the same benefit of the doubt we'd want for ourselves.
We need to distinguish between healthy skepticism and destructive paranoia. Between holding people accountable and tearing them down. Between being vigilant and being looters.
The fiat system is the real enemy here. It's massive, entrenched, and infinitely resourcesful. It will adapt, co-opt, and corrupt everything it touches. Fighting it requires builders who are willing to get their hands dirty, navigate imperfect systems, and make pragmatic compromises while holding onto their core values.
We can continue to be looters, tearing down what we don't understand and driving our best builders toward their own version of Atlantis. Or we can be what we claim to be: supporters of the free market, believers of proof of work, and champions of those building the future.
Don't trust. Verify. But remember: verification works both ways.
-
 @ 3eab247c:1d80aeed
2025-06-05 08:51:39
@ 3eab247c:1d80aeed
2025-06-05 08:51:39Global Metrics
Here are the top stats from the last period:
- Total Bitcoin-accepting merchants: 15,306 → 16,284
- Recently verified (1y): 7,540 → 7,803 (the rest of our dataset is slowly rotting; help us before it's too late!)
- Avg. days since last verification: 398 → 405 (more mappers, please)
- Merchants boosted: 22 (for a total of 4,325 days, someone is feeling generous)
- Comments posted: 34
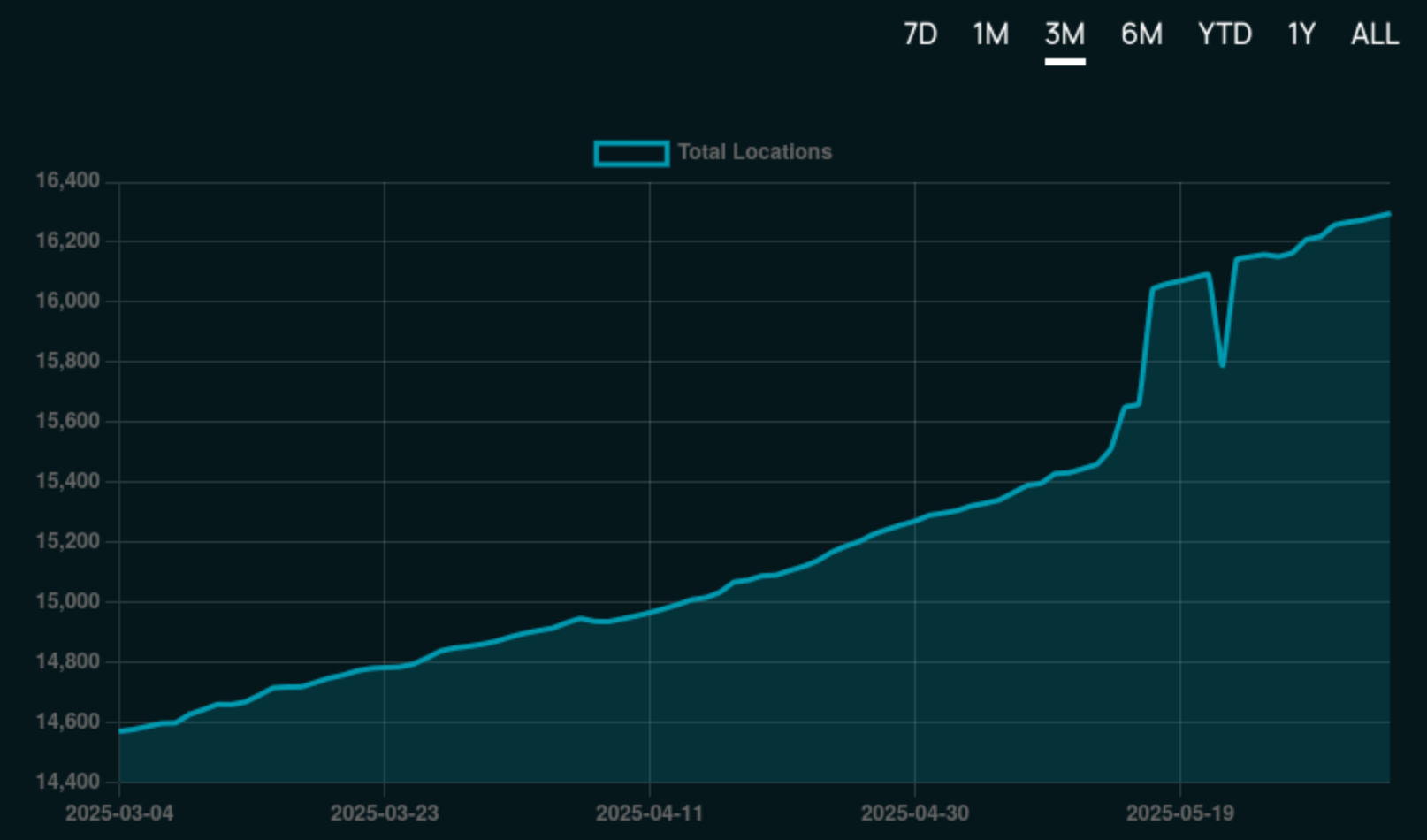
Find current stats over at the 👉 BTC Map Dashboard.
Merchant Adoption
Steak n’ Shake
The US 🇺🇸 is a massive country, yet its BTC Map footprint has been lagging relative to other countries ... that is until now!

In what came as a nice surprise to our Shadowy Supertaggers 🫠, the Steak ’n Shake chain began accepting Bitcoin payments across hundreds of its locations nationwide (with some international locations too).
According to CoinDesk, the rollout has been smooth, with users reporting seamless transactions powered by Speed.
This marks a significant step towards broader Bitcoin adoption in the US. Now to drop the capital gains tax on cheesburgers!
SPAR Switzerland
In other chain/franchise adoption news, the first SPAR supermarket in Switzerland 🇨🇭 to begin accepting Bitcoin was this one in Zug. It was quickly followed by this one in Rossrüti and this one in Kreuzlingen, in what is believed to be part of a wider roll-out plan within the country powered by DFX's Open CryptoPay.
That said, we believe the OG SPAR crown goes to SPAR City in Arnhem Bitcoin City!
New Features
Merchant Comments in the Web App
Web App users are now on par with Android users in that they can both see and make comments on merchants.
This is powered by our tweaked API that enables anyone to make a comment as long as they pass the satswall fee of 500 sats. This helps keep spam manageable and ensure quality comments.
And just in case you were wondering what the number count was on the merchant pins - yep, they're comments!
Here is an 👉 Example merchant page with comments.
Merchant Page Design Tweaks
To support the now trio of actions (Verify, Boost & Comment) on the merchant page, we've re-jigged the design a little to make things a little clearer.
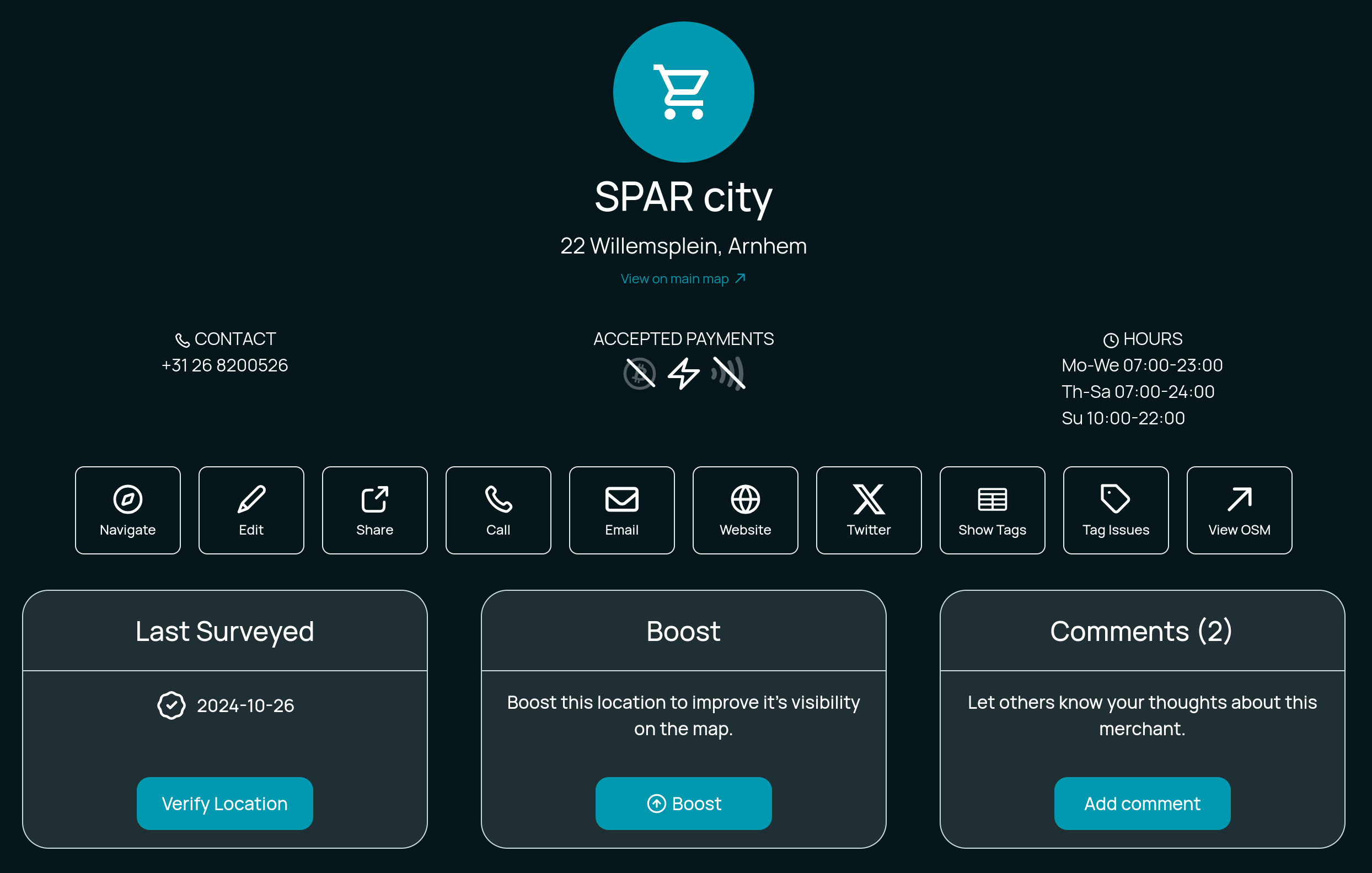
What do you think?
Technical
Codebase Refactoring
Thanks to Hannes’s contributions, we’ve made progress in cleaning-up the Web App's codebase and completing long overdue maintenance. Whilst often thankless tasks, these caretaking activities help immensely with long-term maintainability enabling us to confidently build new features.
Auth System Upgrades
The old auth system was held together with duct tape and prayers, and we’re working on a more robust authentication system to support future public API access. Updates include:
- Password hashing
- Bearer token support
- Improved security practices
More enhancements are in progress and we'll update you in the next blog post.
Better API Documentation
Instead of relying on tribal knowledge, we're finally getting around to writing actual docs (with the help/hindrance of LLMs). The "move fast, break everything" era is over; now we move slightly slower and break slightly less. Progress!
Database Improvements
We use SQLite, which works well but it requires careful handling in async Rust environments. So now we're untangling this mess to avoid accidental blocking queries (and the ensuing dumpster fires).
Backup System Enhancements
BTC Map data comes in three layers of fragility:
- Merchants (backed up by OS - the big boys handle this)
- Non-OSM stuff (areas, users, etc. - currently stored on a napkin)
- External systems (Lightning node, submission tickets - pray to Satoshi)
We're now forcing two core members to backup everything, because redundancy is good.
Credits
Thanks to everyone who directly contributed to the project this period:
- Comino
- descubrebitcoin
- Hannes
- Igor Bubelov
- Nathan Day
- Rockedf
- Saunter
- SiriusBig
- vv01f
Support Us
There are many ways in which you can support us:
-
Become a Shadowy Supertagger and help maintain your local area or pitch-in with the never-ending global effort.
-
Consider a zapping this note or make a donation to the to the project here.
-
 @ 05a0f81e:fc032124
2025-06-05 18:36:08
@ 05a0f81e:fc032124
2025-06-05 18:36:08Akhenaten (originally named Amenhotep IV) was a pharaoh of ancient Egypt known for radically transforming Egyptian religion, art, and culture. He is most famous for promoting the worship of one god—Aten, the sun disk—marking one of the earliest recorded movements toward monotheism.
Early Life and Rise to Power of pharaoh Akhenaten.
The Birth Name was Amenhotep IV, and he was born Around 1380 BCE. By Pharaoh Amenhotep III, and the mother Likely Queen Tiye. He grew up and married a Wife, Nefertiti, one of Egypt's most iconic queens. He have children, Including daughters and likely the father of Tutankhamun (King Tut).
Amenhotep IV ascended the throne around 1353 BCE, succeeding his father, a powerful and prosperous pharaoh, and there was a Religious Revolution.
A Shift Toward Monotheism
Around his 5th regnal year, Amenhotep IV changed his name to Akhenaten, meaning "Effective for Aten".
He abandoned the traditional Egyptian pantheon, especially the powerful god Amun, and elevated Aten as the sole god.
This was a dramatic break from Egypt's deeply rooted polytheistic religion.
The capital city Akhetaten (Modern-day Amarna). Akhenaten moved the capital from Thebes to a new city he built from scratch: Akhetaten (Horizon of Aten).
The city was dedicated entirely to the Aten religion and became a center of art, culture, and politics.
Nefertiti was not just a queen but a powerful co-ruler. Some theories suggest she may have ruled independently for a time after Akhenaten’s death (possibly as Neferneferuaten).
They had at least six daughters. The identity of Akhenaten's sons is debated, but Tutankhamun is widely believed to be his son, possibly by a secondary wife.
Decline and Death
Akhenaten died around 1336 BCE after a 17-year reign.
After his death, his successors (including Tutankhamun) restored traditional religion, abandoned Atenism, and moved the capital back to Thebes.
His monuments were defaced, and his name was erased from king lists, a process known as damnatio memoriae (damnation of memory).
Legacy
Akhenaten is remembered as:
A visionary who introduced monotheism before it appeared in other cultures.
A heretic who defied over a thousand years of religious tradition.
A reformer whose bold changes caused cultural upheaval.
His religious revolution was short-lived, but modern historians and archaeologists regard him as one of the most fascinating and controversial figures in ancient history.
The reasons why Pharaoh Akhenaten introduced monotheism, the worship of Aten, the sun disk, as the one true god are still debated by historians, but several key political, religious, personal, and philosophical factors likely contributed.
✅ Main Reasons Why Akhenaten Introduced Monotheism
- Religious Reform: Belief in a Universal Power
Akhenaten may have genuinely believed in Aten as the supreme creator and life-giver.
The sun was already important in Egyptian religion (Ra, Amun-Ra), but Akhenaten stripped away all personification, choosing the sun's disk (Aten) as a pure, abstract symbol of divine power.
He saw Aten as omnipresent, providing light and life to everything and everyone equally.
- Political Motivation: Weaken the Power of the Priests
The priesthood of Amun at Thebes had become extremely wealthy and powerful, almost a state within a state. By elevating Aten and banning Amun's worship, Akhenaten dismantled the influence of the Amun priests and centralized religious power in his own hands. He made himself the sole mediator between Aten and the people, increasing royal control.
- Personal Vision and Identity
Akhenaten may have had a personal religious experience or conviction that shaped his devotion to Aten.
His new name, “Akhenaten,” meaning “Effective for the Aten,” reflects a deep, personal connection to this god.
He often depicted himself and his family in direct contact with Aten, showing a highly intimate and unique belief system.
- Philosophical and Artistic Shift
Akhenaten's reign saw a revolution in art, emphasizing naturalism, emotion, and individuality.
This change in thinking may reflect a broader philosophical shift toward a more abstract and spiritual understanding of the divine unified in Aten.
Atenism removed the idea of gods with human forms, replacing them with a universal force (the sun's light).
- Reaction Against Religious Corruption or Complexity
Traditional Egyptian religion had hundreds of gods, rituals, and temple hierarchies.
Akhenaten may have seen the system as corrupt, ritualistic, and too complex for ordinary people.
Atenism was simple, focused, and accessible, with the sun’s light reaching everyone equally.
- Political Instability or Health Issues (Speculative)
Some theories suggest Akhenaten’s appearance (depicted with elongated head, wide hips, etc.) may reflect a genetic disorder (e.g., Marfan syndrome or Froehlich's syndrome).
If he was sickly, he may have been drawn to religious introspection or spiritual reform.
Others suggest that political instability or unrest during his early reign may have motivated a bold unifying reform.
Summary
Akhenaten’s monotheism was unprecedented in Egypt’s long religious history. Whether he was a spiritual visionary, a political tactician, or both, his religious revolution stands out as one of the most dramatic and controversial in ancient history.
-
 @ 527337d5:93e9525e
2025-06-05 03:09:02
@ 527337d5:93e9525e
2025-06-05 03:09:02The Algorithmic Pursuit of Connection: A Five-Book Journey into the Self
As a researcher, hitting my thirties and the winding down of a significant project prompted a crucial re-evaluation of life's latter half. While I'd successfully applied probabilistic control theory to one-on-one interactions, the complexities of group dynamics remained a persistent challenge. My recent dive into five diverse books on human relationships inadvertently became a profound journey of self-discovery, fundamentally reshaping my perspective on social connections.
Neil Strauss: A Mirror Reflecting the Self's Evolution
Neil Strauss's The Truth resonated deepest among my recent reads. The author's battle with sex addiction uncomfortably mirrored my own past struggles: the fragile self-esteem stemming from rejection, the hubris born of early successes, and the tendency to view women as mere objects of manipulation. It felt eerily prescient, a glimpse into a potential future.
Yet, I found myself arriving at Strauss's ultimate conclusion – the paramount importance of self-preparation and community – far sooner than he did. This acceleration wasn't accidental; it was the result of intense focus on individual experiences, meticulously replayed and analyzed in my mind. The book, therefore, served less as a revelation and more as a powerful validation of my own journey of introspection and root-cause analysis.
Quantifying Connection: The Promise and Limits of Mathematical Models
Hannah Fry's The Mathematics of Love offered a kindred spirit in its attempt to quantify human relationships. While I appreciate the mathematical lens, Fry's models primarily concern dyadic relationships (N=2), relying on relatively simple systems of two-variable ordinary differential equations. For me, these are akin to linear models, sufficient only up to a certain point. Beyond N=4, the dependencies become exponentially complex.
My own pursuit extends to understanding and optimizing group dynamics within complex systems. This involves multi-variable problems (N $\ge$ 3) and the application of network theory, a far more sophisticated approach. Human collectives, after all, are systems of nodes and edges, where information propagates in predictable ways. My focus is on deriving optimal behavioral controls within these intricate frameworks.
Conversely, Men Are from Mars, Women Are from Venus initially struck me as bordering on conspiracy theory. However, its latter half proved unexpectedly useful. Its clear enumeration of male and female desires, and its articulation of common points of conflict, presented a practical template for communication styles. In a systemic view, this serves as a rudimentary, yet functional, interface design for complex social interactions.
A Dispassionate Critique of Relationship Dogma
My drive for efficiency and systematic understanding led to a rather blunt assessment of certain relationship classics. The New Science of Adult Attachment felt disorganized and frustratingly anecdotal. Lacking a coherent theoretical framework, it burdened the reader with deciphering meaning from a jumble of examples. Its inefficiency was, frankly, its most irksome flaw.
Similarly, Dale Carnegie's How to Win Friends and Influence People struck me as closer to pseudoscience than social science. Its plethora of specific anecdotes obscured any underlying principle. Given my deep engagement with social engineering – a discipline that systematically and practically analyzes human interaction – Carnegie's work appeared largely irrelevant and inefficient. From my perspective, which views humans as objective systems to be analyzed with mathematical rigor, such unstructured approaches hold little value.
The Unveiling of a Core Principle: Humans as Systems
This intensive reading period solidified my most crucial insight: humans, at their core, are systems. This understanding allows for a dispassionate, methodical approach to human collectives, mitigating unnecessary emotional friction.
This revelation has sharply refined my future learning trajectory. I'm now prioritizing foundational theories like graph theory and network theory over anecdotal accounts of human behavior. By mastering these theoretical underpinnings, I aim to precisely model complex human interactions as systems of nodes and edges, enabling the derivation of optimal behavioral controls within communities.
My choice of the term "target for capture" for individuals stems from a personal aversion to perceived equality in certain human interactions, a mechanism to avoid cognitive dissonance. This rational approach, I believe, is key to cultivating secure attachment styles – relationships demonstrably sustainable in the long term. My philosophy is to strategically approach the initial engagement, then transition to a stable, enduring connection. It's a calculated, dispassionate method for achieving desired relational outcomes.
Ultimately, this period of reading wasn't just about acquiring knowledge; it was a profound journey of self-discovery, clarifying my personal frameworks for navigating life's complexities and forging meaningful, yet strategically managed, connections.
-
 @ e4950c93:1b99eccd
2025-06-05 10:23:39
@ e4950c93:1b99eccd
2025-06-05 10:23:39Marques
Nordkidz est une marque allemande qui crée à la demande des vêtements et linges pour les bébés, les enfants, et un peu pour leurs parents.
Matières naturelles utilisées dans les produits
⚠️ Attention, certains produits de cette marque contiennent des matières non naturelles, dont :
Catégories de produits proposés
Cette marque propose des produits intégralement en matière naturelle dans les catégories suivantes :
Vêtements
- Tailles vêtements : bébés, enfants, unisexe
- Hauts : pulls, t-shirts
- Bas : pantalons, pantalons de survêtement, shorts
- Tête et mains : bonnets, écharpes
Maison
- Linge : housses de pouf, langes, ponchos de bain
Autres informations
👉 En savoir plus sur le site de la marque
Où trouver leurs produits ?
- Nordkidz (en allemand, zone de livraison : Allemagne et Union Européenne) 💚 Via ce lien vous soutenez directement la marque.
📝 Tu peux contribuer à cette fiche en suggérant une modification en commentaire.
🗣️ Tu utilises des produits de cette marque ? Partage ton avis en commentaire.
⚡ Heureu-x-se de trouver cette information ? Soutiens le projet en faisant un don pour remercier les contribut-eur-ice-s.
-
 @ 2e8970de:63345c7a
2025-06-05 16:07:04
@ 2e8970de:63345c7a
2025-06-05 16:07:04https://x.com/jburnmurdoch/status/1930203297396249067
https://www.dropbox.com/scl/fi/1lp1dwzx608xdu8jfpkqk/FT_GENDER_DIVIDE_SXSW.pptx?rlkey=9gcwvn77zss3k5l5vgiquennl&e=1&st=apgyr3ug&dl=0
https://stacker.news/items/998014
-
 @ df478568:2a951e67
2025-06-05 23:34:01
@ df478568:2a951e67
2025-06-05 23:34:01About 156,000 blocks ago, I went to a Taco Shop for a bitcoin meetup. I asked my favorite question, “Do you accept bitcoin?”
“Yes," he said as he handed me a Toast Terminal with a BTCpayServer QR code.
 ]
]Awesome!
12,960 blocks later, I took my dad to the taco shop. We ordered food. I asked my favorite question once again.
“Uh…Yeah, but I don't know how to work the machine.”
"Dough!🤦"
It's been a problem in the past, but now lightning payments are about to be ubiquitous. Steak N Shake is taking bitcoin using Speed Wallet and Block is implementing bitcoin payments by 2026 in all legal jurisdictions. I have tested both of these so you don't have to. Just kidding. I geek out on this stuff, but both work great. You can pay with your sats by scanning a screen on a QR code. The employees don't need to be bitcoin lightning network experts. You can just pay as easy as a credit card.
There were 35,000 people at the bitcoin conference, and 4,187 transactions were made. It was a world record. Wait, I thought they said there could only be 7 transactions per second! No, not anymore. Now we can use bitcoin for shopping. I can pay for tacos at taco trucks.

How You Can Accept Bitcoin At Your Business
Coinos is a simple bitcoin point of sale information that acts like a cash register. Bitcoin is peer-to-peer electronic cash. Coinos is a cash register and you should treat it as such. If you make a few hundred thousand sats at the end of the night, you should sweep the bitcoin into your own wallet.. You can use Aqua, AlbyHub, Bull Bitcoin wallet, or whatever your favorite lightning enabled wallet is to withdraw. You'll need a password. Do not lose this. I have tried the automatic withdraws, but it did not work for me. I'm no concerned because this is not a wallet I intend to keep a lot of sats in for a long time.
Here is my coinos payment terminal.
https://coinos.io/ZapthisBlog/receive
I made the QR code with libreqr.com/

Now I have an online bitcoin cash register. The Bitcoiners know how to pay for stuff with sats. They will be proud to show you too. If you're nerdy, you can use all the cool kid tools now, but we will just focus on the lightning address. Anyone can send you sats with a lightning address with just a QR code.
At the end of the night, you cash out to your own wallet. Again, this assumes you have an Aqua Wallet or any other lightning enabled wallet, but all it takes to accept bitcoin at your brick and mortar store is to create an account with Coinos and print out a QR code. It's a quick and easy way to start accepting bitcoin even if you don't expect many clients to shop with sats.
Tips
This is not just a cash register. Employees can also make their own Coinos wallet and receive tips from bitcoiners. Anyone can accept payments using this system. Your kids could use it to sell lemonade for sats. You are only limited by your imagination. When will you begin accepting bitcoin payments? It is easier than ever. You do not need to train employees. You do not need to be in the store. Bitcoin is peer-to-peer electronic cash so you can give it away like cash. I don't know what the tax rules on cash are. You need to verify that with your own jurisdiction. This is not financial or tax advice. This is for informational purposes only.
Remember, this is a custodial wallet. Not your keys not your bitcoin. Don't keep more sats than you are willing to lose on custodial wallets. Sweep your wallet early and often. Loss of funds is possible. There is a small fee for liquidity management too. Do your own research.
-
 @ e2c72a5a:bfacb2ee
2025-06-05 17:14:50
@ e2c72a5a:bfacb2ee
2025-06-05 17:14:50The silent revolution: Ethereum's pivot to 'digital oil' could redefine crypto's future. While Bitcoin grabs headlines as digital gold, Ethereum is quietly transforming into something potentially more valuable—the essential infrastructure powering our digital economy. Ryan Berckmans reveals Ethereum's strategic shift from being just another cryptocurrency to becoming the foundation for stablecoins, tokenized assets, and global financial systems. With $480 billion in stablecoin volume and institutional players entering the space, Ethereum isn't just competing with Bitcoin—it's creating an entirely different value proposition. The question isn't whether ETH will hit $3K, but whether we're underestimating its long-term potential as the backbone of digital finance. Are you positioning yourself for the real crypto revolution happening right under our noses?
-
 @ 58537364:705b4b85
2025-06-05 15:55:12
@ 58537364:705b4b85
2025-06-05 15:55:12อารมณ์ คือ โลก - โลก คือ อารมณ์ อารมณ์ ในโลกปัจจุบันรวมอยู่ที่ วัตถุนิยม อารมณ์ จึงเป็นปัจจัยแห่งเหตุการณ์ทุกอย่างในโลก
…. “ เดี๋ยวนี้คําว่า “อารมณ์” ในภาษาไทยนั้น หมายถึงความรู้สึกในใจมากกว่า; เช่น พื้นเพของจิตใจในขณะนั้นเป็นอย่างไร, เรียกว่าอารมณ์ของเขาเป็นอย่างไร, อารมณ์กําลังดี อารมณ์กําลังไม่ดี, นี่ คําว่าอารมณ์ในภาษาไทยใช้กันไปเสียอย่างนี้ ; มันคนละเรื่องกับในภาษาบาลี ซึ่งคําว่า “อารมณ์” หมายถึง สิ่งที่จะเข้ามากระทบ ตา หู จมูก ลิ้น กาย ใจ.
…. ถ้ากระทบแล้วเกิดความรู้สึกอย่างไร งุ่นง่านอยู่ในใจ อันนั้นไม่ได้เรียกว่าอารมณ์; อันนั้นก็เรียกว่ากิเลสอย่างอื่น เช่น เรียกว่าตัณหาบ้าง อุปาทานบ้าง; ถ้าจัดเป็นพวกขันธ์ ก็เรียกว่า เวทนาขันธ์บ้าง สัญญาขันธ์บ้าง สังขารขันธ์บ้าง; ถ้าเป็นความคิดที่งุ่นง่านก็เรียกว่า “สังขารขันธ์” ทั้งนั้น ดังนั้น เราจะต้องถือเอาคําว่าอารมณ์ในบาลีมาเป็นหลัก …. คําว่า อารมณ์ ที่จะเข้าใจกันง่ายๆ ก็หมายความว่า รูป เสียง กลิ่น รส โผฏฐัพพะ ที่จะมากระทบ ตา หู จมูก ลิ้น กาย นี้ ๕ อย่าง แล้วก็ความรู้สึกเก่าแก่ที่จะมาผุดขึ้นในใจอีก เรียกว่า ธัมมารมณ์ ที่จะมากระทบใจในปัจจุบันนี้ นี้ก็เป็นอันหนึ่ง เลยได้เป็นอารมณ์ ๖. อารมณ์กระทบ ตา หู จมูก ลิ้น กาย ๕ อย่างข้างนอกนี้ก็สําคัญไปพวกหนึ่ง ที่ปรุงขึ้นภายในสําหรับกระทบใจโดยไม่ต้องอาศัย ตา หู จมูก ลิ้น กาย ใจ เลย ในเวลานั้นก็ยังมีอยู่นี้เรียกว่าธัมมารมณ์ นี้ก็ยิ่งสําคัญ: แต่ว่ารวมกันแล้วก็เรียกว่า อารมณ์ ได้ด้วยกันทั้งนั้น แปลว่า สิ่งที่จะมากระทบกับ ตา หู จมูก ลิ้น กาย ใจ นั่นเอง
…. นี้ ดูให้ละเอียดตามตัวหนังสือ คําว่า “อารมณ์” แปลว่า ที่หน่วงบ้าง แปลว่า ที่ยินดีบ้าง, มันมีความหมายละเอียดมาก. ถ้าถือเอาความหมายอย่างคนที่มีตัวตนเป็นหลัก ธรรมะในฝ่ายฮินดูหรือฝ่ายพรหมณ์เขาก็จะพูดว่า สําหรับจิตหรืออาตมันเข้าไปจับฉวยเอา. แต่ถ้าพูดอย่างภาษาชาวพุทธพูดอย่างนั้นไม่ได้ เพราะไม่มีจิตไม่มีอาตมันชนิดนั้น แล้วจิตนี้ก็เพิ่งเกิดขึ้นหลังอารมณ์กระทบแล้ว; เลยต้องพูดตามพระบาลีที่ว่า อาศัยตาด้วย อาศัยรูปด้วย ย่อมเกิดจักษุวิญญาณ; ตาอาศัยกับรูปคืออารมณ์นั้นได้แล้วจึงจะเกิดจักษุวิญญาณ วิญญาณหรือจิตนี้เกิดทีหลัง
…. ฉะนั้น จึงไม่พูดว่า อารมณ์นี้เป็นสิ่งสําหรับจิตหรือตัวตนเข้าไปจับฉวยยึดเอา; ถ้าพูดอย่างนั้นมันก็จะเป็นฮินดูหรือพราหมณ์ไป คือมีตัวตนไป. พูดอย่างพุทธไม่มีตัวตน ทุกอย่างไม่ใช่ตัวตน เป็นสักว่าธาตุ, ได้การปรุงแต่งที่เหมาะแล้วมันก็ปรุงแต่งเป็นสิ่งใหม่ขึ้นมา ในนั้นอาจจะมีความรู้สึกโง่ไปว่าเป็นตัวเราก็ได้
…. ฉะนั้น คําว่าอารมณ์ ถ้าถือตามหลักในทางพุทธศาสนา ก็แปลว่า สิ่งที่อาศัยกันกับจิต จะเรียกว่าเป็นที่หน่วงของจิตมันก็ยังได้: ถ้าเข้าใจผิดมันก็ผิดได้: เรียกว่าสิ่งที่อาศัยกับอายตนะ แล้วก็เกิดเป็นความรู้สึกเป็นจิตขึ้นมา จิตกําลังหน่วงสิ่งนั้นเป็นอารมณ์ก็ได้ แต่จะให้เป็นตัวตนนั้นไม่ได้
…. โดยพยัญชนะก็มีอยู่อย่างนี้ ตัวพยัญชนะก็ยังกํากวม อารมฺมณํ หรือที่มาจาก อาลมฺพนํ ก็แปลว่า ที่หน่วงของจิต. ถ้าจะถือว่ามาจาก รม ที่แปลว่า ยินดี ก็แปลว่า มันเป็นสิ่งที่หลงใหลยินดีของจิต อย่างนี้ก็ยังได้อีก
…. แต่ขอให้รู้จักจากภายในดีกว่าที่จะมารู้จักจากตัวหนังสือ เมื่อตากระทบรูป เมื่อหูกระทบเสียง เป็นต้น มันเกิดขึ้นในใจ, แล้วสังเกตเอาที่นั่นก็แล้วกัน ว่ารูปที่มากระทบตานั้นมันคืออะไร? เสียงที่มากระทบหูนั้นมันคืออะไร? จะค่อยเข้าใจแจ่มแจ้งขึ้นทีละน้อยๆ ว่าอารมณ์นั้นคืออะไร? แต่ให้เข้าใจไว้ทีหนึ่งก่อนว่าสิ่งที่เรียกว่าอารมณ์ๆที่มากระทบนี้ มันยังไม่ดีไม่ชั่ว ยังไม่จัดเป็นสิ่งดีสิ่งชั่ว มันต้องผสมปรุงแต่งเป็นความคิดอย่างนั้นอย่างนี้เสียก่อน จึงจะจัดเป็นดีเป็นชั่ว อารมณ์ล้วนๆยังไม่ดีไม่ชั่ว จะได้รู้จักป้องกัน อย่าให้เป็นไปในทางชั่ว, ให้เป็นไปแต่ในทางดีได้ตามปรารถนา
…. นี้เรียกว่าโดยพยัญชนะ โดยตัวหนังสือ คําว่า “อารมณ์” แปลว่า เป็นที่ยินดีแห่งจิต, เป็นที่ยึดหน่วงแห่งจิต; โดยเฉพาะภาษาอภิธรรมแล้วก็ใช้คําว่า “เป็นที่หน่วงเอาของจิต”, คือจิตย่อมหน่วงสิ่งใดสิ่งหนึ่งเป็นอารมณ์ แปลคําว่าอารมณ์บ้าง, อาลัมพนะ แปลว่า เป็นที่หน่วงเอา.
…. เดี๋ยวนี้เราเรียนพุทธศาสนาไม่ใช่เรามาเรียนหนังสือบาลี, เราจะเรียนพระธรรมคําสอนของพระพุทธเจ้า เราก็ต้องดูสิ่งที่เรียกว่าอารมณ์ โดยหลักของธรรมชาติที่ปรุงแต่งกันอยู่ในใจดีกว่า; ก็อย่างพระบาลีที่ได้ว่ามาแล้วข้างต้นว่า จกฺขุญฺจ ปฏิจฺจ รูเป จ อุปฺปชฺชติ จกฺขุวิญฺญาณํ = เพราะอาศัยตาด้วย รูปด้วย ย่อมบังเกิดจักษุวิญญาณ ติณฺณํ ธมฺมานํ สงฺคติ ผสฺโส - การประจวบกันของ ๓ สิ่งนี้เรียกว่า “ผัสสะ”, ผสฺสปจฺจยา เวทนา = เพราะผัสสะเป็นปัจจัยจึงเกิดเวทนา, อย่างนี้เรื่อยไปจนเกิดทุกข์ จนเกิดความทุกข์, นี้เรียกว่าโดยธรรมชาติ
…. สิ่งที่เรียกว่าอารมณ์มีอยู่โดยธรรมชาติที่จะเข้ามาอาศัยกันกับตาข้างใน ที่มีอยู่ในตัวคน. แล้วจะเกิดจักษุวิญญาณ เป็นต้น ขึ้นในตัวคน; จะเกิด ผัสสะ เวทนา ตัณหา อุปาทาน ภพ ชาติ ขึ้นในตัวคน; นี้โดยธรรมชาติ พระพุทธเจ้าท่านบันดาลอะไรไม่ได้ : ธรรมชาติเป็นอยู่อย่างนี้ แต่ท่านรู้เรื่องนี้ท่านจึงนํามาสอนว่า ธรรมชาติมันมีอยู่อย่างนี้ เราจะต้องเข้าใจให้ถูกต้อง โดยที่จะป้องกันความทุกข์ไม่ให้เกิดขึ้นมาได้, หรือถ้าเกิดขึ้นมาได้ก็จะดับเสียได้
…. เราควรจะรู้จักอารมณ์ในฐานะที่เป็นธรรมชาติอันหนึ่ง ที่มีอยู่ตามธรรมชาติ แล้วที่จะเข้ามาทําเรื่องทําราวขึ้นในจิตใจของคนเราให้เกิดปัญหายุ่งยากนี้ให้ดีๆ นี้เรียกว่ารู้จักอารมณ์จากธรรมชาติโดยตรงอย่างนี้ ดีกว่าที่จะรู้จักตามตัวหนังสือ, ดีกว่าที่จะรู้จักตามคําบอกเล่าบางอย่างบางประการที่มันไม่มีประโยชน์อะไร. รู้จักตามคําบอกเล่าก็รู้จักตามที่พระพุทธเจ้าท่านตรัสดีกว่า แต่แล้วยังไม่รู้จักตัวจริง จนกว่าจะมารู้จักจากที่เมื่ออารมณ์มากระทบตา หู จมูก ลิ้น กาย ใจ เข้าจริงๆ : นั่นจึงจะรู้จักอารมณ์ รู้จักผลที่เกิดขึ้นจากการกระทบของอารมณ์, รู้จักต่อไปตามลําดับ จนแก้ปัญหาต่างๆ ได้
…. นี่ ขอร้องให้รู้จักสิ่งที่เรียกว่า อารมณ์ ในฐานะที่เป็นธรรมชาติอันหนึ่ง ที่มีอยู่ตามธรรมชาติ ที่จะเข้ามากระทบอายตนะภายใน คือ กระทบ ตา หู จมูก ลิ้น กาย ใจ แล้วมีเรื่องมีราวมีปัญหา
อารมณ์ คือ โลก - โลก คือ อารมณ์ …. “ ที่นี้จะให้ดูต่อไปอีก ว่าโดยข้อเท็จจริงที่เป็นอยู่แล้ว อารมณ์นั้นคืออะไร? ถ้าจะพูดโดยข้อเท็จจริงหรือตามสถานการณ์ที่เป็นอยู่จริงในชีวิตของคนเรา อารมณ์มันก็คือ “โลก” นั่นเอง. เดี๋ยวนี้เราไม่รู้จักโลกในฐานะอย่างนี้, เราไปเข้าใจความหมายของคําว่าโลกแคบไปบ้าง หรือว่าเขวไปบ้าง.
…. ถ้าจะรู้ตามหลักพระพุทธศาสนาแล้ว โลกทั้งหมดก็คือสิ่งที่จะมาปรากฏแก่ ตา หู จมูก ลิ้น กาย ใจ ของเรา, เรามีเพียง ๖ อย่าง, แล้วมันก็ ปรากฏได้เพียง ๖ ทาง, มากกว่านั้นมันปรากฏไม่ได้ ดังนั้น โลกก็คือสิ่งที่จะมาปรากฏแก่ ตา หู จมูก ลิ้น กาย ใจ ๖ อย่างของเรา. “โลก” ก็คือ รูป เสียง กลิ่น รส โผฏฐัพพะ ธัมมารมณ์ ๖ ประการเท่านั้น, ไม่มีอะไรมากไปกว่านั้น
…. ฉะนั้น รูป เสียง กลิ่น รส โผฏฐัพพะ ธัมมารมณ์ แต่ละอย่าง ๆ ก็คือ โลกในแต่ละแง่ละมุม นั่นเอง, ที่เป็น รูป เสียง กลิ่น รส โผฏฐัพพะ ก็อยู่ข้างนอก จะเรียกว่าอยู่ข้างนอกก็ได้, ที่เป็นอารมณ์เกิดขึ้นในใจ ปรุงขึ้นในใจก็เรียกว่าโลกข้างในก็ได้ แต่มันก็เป็นโลกอยู่นั่นแหละ เพราะมันเป็นสิ่งที่จิตจะต้องรู้สึก จิตรู้สึกก็เรียกว่าโลกสําหรับจิต ตา หู จมูก ลิ้น กาย รู้สึก ก็เรียกว่าโลกสำหรับ ตา หู จมูก ลิ้น กาย. นี้ขอให้มองให้เห็นชัดตามพระพุทธประสงค์ว่า โลก ก็คือ อารมณ์, อารมณ์ ก็คือ โลก.
…. แต่ทีนี้ พระพุทธเจ้าท่านมองลึกกว่านั้น ท่านตรัสถึงข้อที่ว่า ถ้ามันมาเกิดเป็นปัญหาแก่เราเมื่อไรจึงจะเรียกว่า “มันมี” พอมันมาเป็นปัญหาแก่เราเมื่อไรก็เรียกว่า “เป็นทุกข์”; เพราะว่าเราได้ไปจับฉวยยึดถือเอาตามประสาตามวิสัยของคนที่ไม่รู้จักโลก ถ้าพูดว่าไม่รู้จักโลกแล้วคนก็มักจะไม่ยอมรับ เพราะว่าเขาจะพูดว่าเขารู้จักโลกดี. ยิ่งพวกฝรั่งสมัยนี้ นักวิทยาศาสตร์ปราดเปรื่องนั้น เขาจะไม่ยอมรับว่าเขาไม่รู้จักโลก. แต่ถ้าพูดตามหลักพุทธศาสนาแล้วก็จะพูดได้ว่ายังไม่รู้จักโลกเลย เป็นคนตาบอดยิ่งกว่าตาบอด; เพราะว่าฝรั่งเหล่านั้นรู้จักโลกแต่ในแง่สําหรับจะยึดมั่นถือมั่นเป็น “ตัวกู ของกู” จะครองโลกจะอะไร เอาประโยชน์ทุกอย่าง; เขารู้จักโลกในแง่นี้ อย่างนี้พุทธบริษัทไม่เรียกว่า “รู้จักโลก”; แต่ถือว่าเป็นคนตาบอดต่อโลก, หลงยึดมั่นถือมั่นในโลก. เพราะว่าคนเหล่านั้นไม่รู้จักโลกโดยความเป็นอารมณ์ ๖ ประการ คือ รูป เสียง กลิ่นรส โผฏฐัพพะ ธัมมารมณ์, แล้วเป็น “มายา” คือ เอาจริงไม่ได้ เป็นของชั่วคราวๆ หลอกให้เกิดความรู้สึกยึดมั่นถือมั่น
…. นี้เรารู้จัก เราไม่ไปหลงยึดมั่นถือมั่นกับมัน นี้จึงเรียกว่า “คนที่รู้จักโลก” ไปตามหลักของพุทธศาสนา, ฉะนั้น จึงไม่ยึดมั่นถือมั่นสิ่งใดโดยความเป็นตัวตน หรือโดยความเป็นของตน, เรียกว่าเป็นผู้รู้จักอารมณ์ ๖ ประการนั้นก็คือรู้จักโลกทั้งปวง, แล้วก็ไม่หลงไปในโลกในแง่ใดแง่หนึ่ง นี้เรียกว่า อารมณ์ ก็คือ โลก นั่นเอง ในความหมายที่ลึกที่สุดของพระพุทธสาสนา ไม่ใช่โลกก้อนดิน, ไม่ใช่โลกก้อนกลมๆ นี้. แต่มันหมายถึงคุณค่าอะไรที่มันมีอยู่ในโลกกลมๆ นี้ ที่จะเข้ามามาทําให้เกิดปัญหา ที่ตา ที่หู ที่จมูก ที่ลิ้น ที่กาย ที่ใจ ของคน. นั่นแหละคือตัวร้ายกาจของสิ่งที่เรียกว่า โลก เราจะต้องรู้จักในส่วนนี้ให้เพียงพอ
อารมณ์ในโลกปัจจุบันมารวมที่วัตถุนิยม …. ทีนี้ ดูอีกแง่หนึ่งก็โดยปัญหาที่กําลังมีอยู่ อารมณ์ในโลกนี้ในฐานะที่มันเป็นตัวปัญหาที่กําลังมีอยู่ มันมารวมอยู่ที่คําว่า “วัตถุนิยม”: หมายความว่า ตา หู จมูก ลิ้น กาย ใจ นี้ มันเป็นฝ่ายชนะ ไปหลงใหลในอารมณ์ รูป เสียง กลิ่น รส โผฏฐัพพะ ฯลฯ, แล้วก็เกิดนิยมหลงใหลในวัตถุเหล่านั้น จนเกิดความคิดใหม่ๆ, ปรุงแต่งไปในทางที่จะให้หลงใหลในโลกยิ่งขึ้นๆ, ความเจริญก้าวหน้า ในโลกสมัยนี้เป็นไปแต่ในทางอย่างนี้ ฉะนั้น จึงไกลความสงบ, ไกลสันติภาพ ไกลอะไรออกไปทุกที. การที่มนุษย์ที่มีปัญญาในโลกสมัยนี้ โดยเฉพาะฝรั่งที่ก้าวหน้านั้นเขาก็จัดโลกไปแต่ในแง่ของวัตถุมากขึ้นๆ: มันก็ไกลจากสันติภาพ ไกลจากความสงบสุขยิ่งขึ้นทุกที
…. ความสะดวกสบายที่ทําให้เกิดขึ้นมาได้นั้น ไม่ได้ช่วยส่งเสริมเกิดสันติภาพ; แต่มันช่วยให้เกิดความหลงในโลกนั้นเองมากขึ้น แล้วก็ช่วยให้หลงใหลใน “ตัวกู ของกู”, ยึดมั่นถือมั่นเห็นแก่ตัวมากขึ้น รวมกันแล้วมันไม่มีทางที่จะเกิดสันติภาพหรือสันติสุขในโลกได้เลย, จึงกลายเป็นความหลอกลวงเหลือประมาณ โลกจึงกลายเป็นความหลอกลวง, หรือสิ่งที่หลอกลวงเหลือประมาณใน เวลานี้ เราเรียกกันว่า ติดบ่วง หรือว่า ติดเหยื่อของวัตถุนิยม. คําพูดทั้งหมดนี้ ล้วนแต่เป็นการแสดงให้เห็นว่า อารมณ์นี้คืออะไร สิ่งที่เรียกว่าอารมณ์นั้น คือตัวโลกที่กําลังหลอกลวงเราอยู่ทุกวันอย่างยิ่ง โดยเฉพาะในปัจจุบันนี้เป็นวัตถุนิยม นี้คืออารมณ์”
พุทธทาสภิกขุ ที่มา : ธรรมบรรยายภาคมาฆบูชา ครั้งที่ ๗ หัวข้อเรื่อง “อารมณ์ คือ ปัจจัยแห่งเหตุการณ์ทุกอย่างในโลก” เมื่อวันที่ ๑๖ กุมภาพันธ์ ๒๕๑๗ จากหนังสือชุดธรรมโฆษณ์ เล่มชื่อว่า “ก ข ก กา ของการศึกษาพุทธศาสนา”
หมายเหตุ
“อารมณ์ ” ในทางพุทธศาสนา มี ๖ คือ... * ๑. รูปะ = รูป, สิ่งที่เห็น หรือ วัณณะ คือ สี * ๒. สัททะ = เสียง * ๓. คันธะ = กลิ่น * ๔. รสะ = รส * ๕. โผฏฐัพพะ = สัมผัสทางกาย * ๖. ธรรมารมณ์ = สิ่งที่ใจนึกคิด, อารมณ์ที่เกิดกับใจ
…. ทั้ง ๖ อย่างนี้ เป็นสิ่งสำหรับให้จิตยึดหน่วง เรียกอีกอย่างว่า "อายตนะภานนอก" ก็ได้
“อายตนะภายใน ๖” คือ ที่เชื่อมต่อให้เกิดความรู้, แดนต่อความรู้ฝ่ายภายใน มี * ๖ อย่าง คือ... * ๑. จักษุ - ตา * ๒. โสตะ - หู * ๓. ฆานะ - จมูก * ๔. ชิวหา - ลิ้น * ๕. กาย - กาย * ๖. มโน - ใจ
… หรือจะเรียกอีกอย่างว่า “อินทรีย์ ๖” ก็ได้ เพราะเป็นใหญ่ในหน้าที่ของตนแต่ละอย่าง เช่น จักษุ เป็นเจ้าการ(เป็นใหญ่)ในการเห็น เป็นต้น
ท. ส. ปัญญาวุฑโฒ – รวบรวม.
-
 @ e2c72a5a:bfacb2ee
2025-06-05 17:11:03
@ e2c72a5a:bfacb2ee
2025-06-05 17:11:03The $220 million crypto heist that took just minutes reveals a fatal flaw in DeFi security. While blockchain tech promises trustless transactions, the Cetus DEX exploit on Sui exposed how a single undetected bug in a math library became catastrophic. What's truly alarming isn't the hack itself but the revelation from Curve's founder that professional hackers-for-hire are now coordinating sophisticated cross-platform attacks. This signals a dangerous evolution in crypto threats where vulnerabilities aren't just discovered—they're hunted by organized teams with specialized skills. The industry faces a stark choice: invest aggressively in preventative security or watch as billions more vanish in seconds. Is your crypto truly safe, or just waiting for the right hacker to find its weakness?
-
 @ 472f440f:5669301e
2025-06-04 20:58:53
@ 472f440f:5669301e
2025-06-04 20:58:53Marty's Bent
J.P. Morgan CEO Jamie Dimon has long been an outspoken skeptic and critic of bitcoin. He has called Bitcoin a speculative asset, a fraud, a pet rock, and has opined that it will inevitably blow up. A couple of years ago, he was on Capitol Hill saying that if he were the government, he would "close it down". Just within the last month, he was on Fox Business News talking with Maria Bartiromo, proclaiming that the U.S. should be stockpiling bullets and rare earth metals instead of bitcoin. It's pretty clear that Jamie Dimon, who is at the helm of the most powerful and largest bank in the world, does not like bitcoin one bit.
Evidence below:

via Bitcoin Magazine

via me
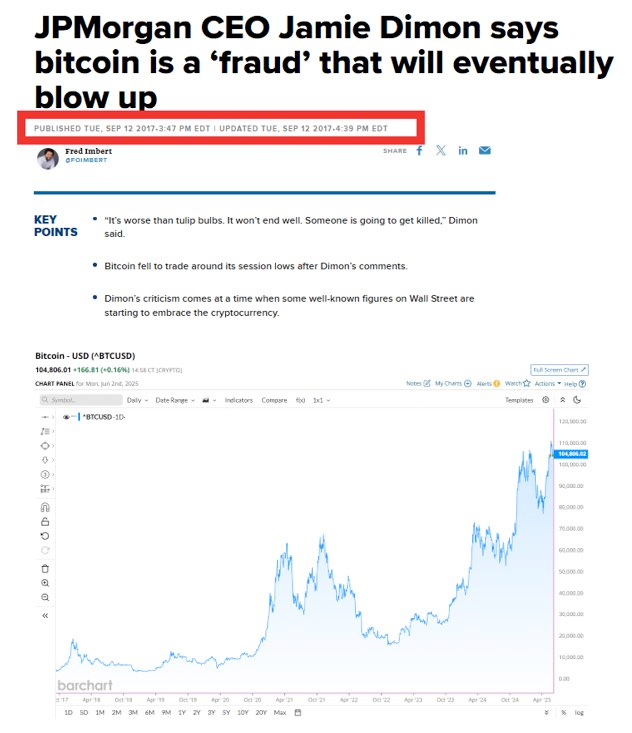
via CNBC

Despite Dimon's distinguished disdain for Bitcoin, J.P. Morgan cannot deny reality. The CEO of the largest bank in the world is certainly a powerful man, but no one individual, even in the position that Jamie Dimon is in, is more powerful than the market. And the market has spoken very clearly, it is demanding bitcoin. The Bitcoin ETFs have been the most successful ETFs in terms of pace of growth since their launch. They've accumulated tens of billions of dollars in AUM in a very short period of time. Outpacing the previous record set by the gold ETF, GLD.
Whether or not Jamie Dimon himself likes Bitcoin doesn't matter. J.P. Morgan, as the largest bank in the world and a publicly traded company, has a duty to shareholders. And that duty is to increase shareholder value by any ethical and legal means necessary. Earlier today, J.P. Morgan announced plans to offer clients financing against their Bitcoin ETFs, as well as some other benefits, including having their bitcoin holdings recognized in their overall net worth and liquid assets, similar to stocks, cars, and art, which will be massive for bitcoiners looking to get mortgages and other types of loans.

via Bloomberg
I've talked about this recently, but trying to buy a house when most of your liquid net worth is held in bitcoin is a massive pain in the ass. Up until this point, if you wanted to have your bitcoin recognized as part of your net worth and count towards your overall credit profile, you would need to sell some bitcoin, move it to a bank account, and have it sit there for a certain period of time before it was recognized toward your net worth. This is not ideal for bitcoiners who have sufficient cash flows and don't want to sell their bitcoin, pay the capital gains tax, and risk not being able to buy back the amount of sats they were forced to sell just to get a mortgage.
It's not yet clear to me whether or not J.P. Morgan will recognize bitcoin in cold storage toward their clients' net worth and credit profile, or if this is simply for bitcoin ETFs only. However, regardless, this is a step in the right direction and a validation of something that many bitcoiners have been saying for years. Inevitably, everyone will have to bend the knee to bitcoin. Today, it just happened to be the largest bank in the world. I expect more of this to come in the coming months, years, and decades.
Lyn Alden likes to say it in the context of the U.S. national debt and the fiscal crisis, but it also applies to bitcoin adoption and the need for incumbents to orient themselves around the demands of individual bitcoiners; nothing stops this train.
Corporate Bitcoin Treasuries are Changing Market Dynamics
Leon Wankum revealed how corporate Bitcoin treasuries are fundamentally reshaping business dynamics. Companies can now issue equity to fund operations while preserving their Bitcoin holdings, creating a revolutionary capital structure. Leon highlighted MicroStrategy's position, noting they hold enough Bitcoin to cover dividend payments for over 200 years. This model enables companies to reduce founder dilution since they don't need repeated funding rounds when their treasury appreciates.
"Some companies' Bitcoin treasuries are now worth more than all money they've ever raised." - Leon Wankum
Leon shared examples from his own portfolio companies where this strategy has proven transformative. Public companies have discovered an entirely new business model through strategic dilution that actually increases BTC per share. As Leon explained, this approach allows firms to leverage equity markets for operational funding while their Bitcoin treasury compounds in value, creating a positive feedback loop that benefits both shareholders and the company's long-term sustainability.
Check out the full podcast here for more on real estate price cycles, Bitcoin lending products, and the transition to a Bitcoin standard.
Headlines of the Day
California May Seize Idle Bitcoin After 3 Years - via X
Semler Scientific Buys $20M More Bitcoin, Holds $467M - via X
US Home Sellers Surge as Buyers Hit 4-Year Low - via X
Get our new STACK SATS hat - via tftcmerch.io
Take the First Step Off the Exchange
Bitkey is an easy, secure way to move your Bitcoin into self-custody. With simple setup and built-in recovery, it’s the perfect starting point for getting your coins off centralized platforms and into cold storage—no complexity, no middlemen.
Take control. Start with Bitkey.
Use the promo code “TFTC20” during checkout for 20% off
Ten31, the largest bitcoin-focused investor, has deployed $150.00M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/invest.
Final thought...
I feel old.
Get this newsletter sent to your inbox daily: https://www.tftc.io/bitcoin-brief/
Subscribe to our YouTube channels and follow us on Nostr and X:
-
 @ cae03c48:2a7d6671
2025-06-05 16:01:20
@ cae03c48:2a7d6671
2025-06-05 16:01:20Bitcoin Magazine
Adam Back Invests SEK 21 Million to H100 Group Bitcoin Treasury StrategyToday, H100 Group AB announced it has entered a SEK 21 million convertible loan from an investment agreement with Adam Back, with the option to expand his investment to SEK 277 million through a five-tranche convertible loan deal. The proceeds will be used to buy Bitcoin in alignment with H100 Group’s long-term Bitcoin treasury strategy.
H100 Group AB (Ticker: H100) secures a SEK 21M ($2.1M) commitment from @adam3us , with rights to invest an additional SEK 128M ($12.8M) in tranches—bringing the total contemplated raise to SEK 277M (~$27.7M). pic.twitter.com/c0HgMSRxut
— H100 (@H100Group) June 3, 2025
Under the agreement, Back may invest up to SEK 128 million across four additional tranches, with guaranteed participation of at least 50%. Each tranche is twice his committed amount, demonstrating his support for H100’s long-term growth.
The press release said, “Adam Back may request the Second Tranche within 90 days from signing of the Initial Tranche, the Third Tranche within 90 days from signing of the Second Tranche, the Fourth Tranche within 90 days from signing of the Third Tranche and the Fifth Tranche within ninety 90 days from signing of the Fourth Tranche. In the event Adam Back does not request a Future Tranche within the deadline, the right to request subsequent Future Tranches lapses.”
The convertible loans have no interest and have a five year maturity. At any time, Back may convert the loans into shares of the Company. Conversion prices are fixed per tranche: SEK 1.75 per share for the initial tranche, rising to SEK 5.00 by the fifth tranche. H100 retains the right to force conversion if the stock price exceeds the conversion rate by 33% over a 20 day period. Full conversion of the initial tranche would result in 12 million new shares and a 9.3% dilution.
“Upon request of a tranche Adam Back is obliged to invest in the relevant Tranche with SEK 15,750,000 in the second tranche, SEK 23,625,000 in the third tranche, SEK 35,437,500 in the fourth tranche, and SEK 53,156,250 in the fifth tranche,” stated the press release. “The contemplated size for each tranche is twice the entitled amount of Adam Back.”
Blockstream has “been around since 2014 and we work with our investors to put Bitcoin in a balance sheet back then and since then,” said Adam Back at the 2025 Bitcoin Conference. “I think the way to look at the treasury companies is that Bitcoin is effectively the hurdle rate; it’s very hard to outperform bitcoin. Most people that have invested in things since bitcoin has been around have thought, ‘oh, I should have put that in bitcoin and not in the other thing.”
This post Adam Back Invests SEK 21 Million to H100 Group Bitcoin Treasury Strategy first appeared on Bitcoin Magazine and is written by Oscar Zarraga Perez.
-
 @ 1c5ff3ca:efe9c0f6
2025-06-05 06:29:45
@ 1c5ff3ca:efe9c0f6
2025-06-05 06:29:45Just calling it Open is not enough - Herausforderungen öffentlicher Bildungsinfrastrukturen und wie Nostr helfen könnte
Ich möchte gerne mit euch teilen, an welchen Konzepten ich arbeite, um die öffentliche Bildungsinfrastruktur mit Hilfe von Nostr zugänglicher und offener zu gestalten. Ich arbeite im Bereich öffentlicher Bildungsinfrastrukturen, besonders im Feld von Open Educational Resources (#OER). OER sind offen lizenzierte Bildungsmaterialien, die mit einer offenen Lizenz, meist einer Creative Commons Lizenz, versehen sind (CC-0, CC-BY, CC-BY-SA). Durch die klare und offene Lizenzierung ist es leicht möglich, die Lernmaterialien auf die individuellen Bedarfe anzupassen, sie zu verbessern und sie erneut zu veröffentlichen.
Seit vielen Jahren wird einerseits die Entwicklung freier Bildungsmaterialien gefördert, andererseits werden Plattformen, insbesondere Repositorien gefördert, die diese Materialien verfügbar machen sollen. Denn irgendwo müssen diese Materialien zur Verfügung gestellt werden, damit sie auch gefunden werden können.
Das klappt allerdings nur so mittelgut.
Herausforderungen
Nach vielen Jahren Förderung kann die einfache Frage: "Wo kann ich denn mein OER-Material bereitstellen" nicht einfach beantwortet werden. Es gibt Services, bei denen ich mein OER hochladen kann, jedoch bleibt es dann eingeschlossen in dieser Plattform und wird nicht auf anderen Plattformen auffindbar. Außerdem sind diese Services häufig an bestimmte Bildungskontexte gebunden oder geben Content erst nach einer Qualitätsprüfung frei. Dies führt dazu, dass ein einfaches und gleichzeitig öffentliches Teilen nicht möglich ist.
Diese und weitere Herausforderungen haben ihren Ursprung darin, dass Service und Infrastruktur in der Architektur öffentlichen Bildungsarchitektur ungünstig vermischt werden. Als Infrastruktur verstehe ich hier die Bereitstellung einer öffentlichen und offen zugänglichen Bildungsinfrastruktur, auf der Daten ausgetauscht, also bereitgestellt und konsumiert werden können. Jedoch existiert eine solche Infrstruktur momentan nicht unabhängig von den Services, die auf ihr betrieben werden. Infrastrukturbetreiber sind momentan gleichzeitig immer Servicebetreiber. Da sie aber die Hand darüber haben wollen, was genau in ihrem Service passiert (verständlich), schränken sie den Zugang zu ihrer Infrastruktur mit ein, was dazu führt, dass sie Lock-In Mechanismen großer Medienplattformen in der kleinen öffentlichen Bildungsinfrastruktur replizieren.
Es ist in etwas so, als würde jeder Autobauer auch gleichzeitig die Straßen für seine Fahrzeuge bauen. Aber halt nur für seine Autos.
Anhand einiger beispielhafter Services, die bestehende Plattformen auf ihren Infrastrukturen anbieten, möchte ich die Herausforderungen aufzeigen, die ich im aktuellen Architekturkonzept sehe:
- Upload von Bildungsmaterial
- Kuration: Zusammenstellung von Listen, Annotation mit Metadaten
- Crawling, Indexierung und Suche
- Plattfformübergreifende Kollaboration in Communities -> Beispiel: Qualitätssicherung (was auch immer das genau bedeutet)
- KI- Services -> Beispiel: KI generierte Metadaten für BiIdungsmaterial
Material Upload
Der Service "Material-Upload" oder das Mitteilen eines Links zu einem Bildungsmaterial wird von verschiedenen OER-Pattformen bereitgestellt (wirlernenonline.de, oersi.org, mundo.schule).
Dies bedeutet konkret: Wenn ich bei einer der Plattformen Content hochlade, verbleibt der Content in der Regel auch dort und wird nicht mit den anderen Plattformen geteilt. Das Resultat für die User: Entweder muss ich mich überall anmelden und dort mein Material hochladen (führt zu Duplikaten) oder damit leben, dass eben nur die Nutzer:innen der jeweiligen Plattform meinen Content finden können.
Der "Open Educational Resource Search Index" (OERSI) geht diese Herausforderung an, indem die Metadaten zu den Bildungsmaterialien verschiedener Plattformen in einem Index bereitgestellt werden. Dieser Index ist wiederum öffentlich zugänglich, sodass Plattformen darüber auch Metadaten anderer Plattformen konsumieren können. Das ist schon sehr gut. Jedoch funktioniert das nur für Plattformen, die der OERSI indexiert und für alle anderen nicht. Der OERSI ist auf den Hochschulbereich fokussiert, d.h. andere Bildungskontexte werden hier ausgeschlossen. Der Ansatz für jeden Bildungsbereich einen passenden "OERSI" daneben zustellen skaliert und schlecht und es bleibt die Herausforderung bestehen, dass für jede Quelle, die indexiert werden soll, ein entsprechender Importer/Crawler geschrieben werden muss.
Dieser Ansatz (Pull-Ansatz) rennt den Materialien hinterher.
Es gibt jedoch noch mehr Einschränkungen: Die Plattformen haben sich jeweils auf spezifische Bildungskontexte spezialisiert. D.h. auf die Fragen: Wo kann ich denn mein OER bereitstellen, muss immer erst die Gegenfrage: "Für welchen Bildungsbereich denn?" beantwortet werden. Wenn dieser außerhalb des allgemeinbildendenden Bereichs oder außerhalb der Hochschule liegt, geschweige denn außerhalb des institutionellen Bildungsrahmens, wird es schon sehr, sehr dünn. Kurzum:
- Es ist nicht einfach möglich OER bereitzustellen, sodass es auch auf verschiedenen Plattformen gefunden werden kann.
Kuration
Unter Kuration verstehe ich hier die Zusammenstellung von Content in Listen oder Sammlungs ähnlicher Form sowie die Annotation dieser Sammlungen oder des Contents mit Metadaten.
Einige Plattformen bieten die Möglichkeit an, Content in Listen einzuordnen. Diese Listen sind jedoch nicht portabel. Die Liste, die ich auf Plattform A erstelle, lässt sich nicht auf Plattform B importieren. Das wäre aber schön, denn so könnten die Listen leichter auf anderen Plattformen erweitert oder sogar kollaborativ gestaltet werden, andererseits werden Lock-In-Effekte zu vermieden.
Bei der Annotation mit Metadaten treten verschiedene zentralisierende Faktoren auf. In der momentanen Praxis werden die Metadaten meist zum Zeitpunkt der Contentbereitstellung festgelegt. Meist durch eine Person oder Redaktion, bisweilen mit Unterstützung von KI-Services, die bei der Metadateneingabe unterstützen. Wie aber zusätzliche eigene Metadaten ergänzen? Wie mitteilen, dass dieses Material nicht nur für Biologie, sondern auch für Sport in Thema XY super einsetzbar wäre? Die momentanen Ansätze können diese Anforderung nicht erfüllen. Sie nutzen die Kompetenz und das Potential ihrer User nicht.
- Es gibt keine interoperablen Sammlungen
- Metadaten-Annotation ist zentralisiert
- User können keine eigenen Metadaten hinzufügen
Crawling, Indexierung und Suche

Da die Nutzer:innen nicht viele verschiedene Plattformen und Webseiten besuchen wollen, um dort nach passendem Content zu suchen, crawlen die "großen" OER-Aggregatoren diese, um die Metadaten des Contents zu indexieren. Über verschiedene Schnittstellen oder gerne auch mal über das rohe HTML. Letztere Crawler sind sehr aufwändig zu schreiben, fehleranfällig und gehen bei Design-Anpassungen der Webseite schnell kaputt, erstere sind etwas stabiler, solange sich die Schnittstelle nicht ändert. Durch den Einsatz des Allgemeinen Metadatenprofils für Bildungsressourcen (AMB) hat sich die Situation etwas verbessert. Einige Plattformen bieten jetzt eine Sitemap an, die Links zu Bildungsmaterial enthalten, die wiederum eingebettet
script-tags vom Typapplication/ld+jsonenthalten, sodass die Metadaten von dort importiert werden können.Beispiel: e-teaching.org bietet hier eine Sitemap für ihre OER an: https://e-teaching.org/oer-sitemap.xml und auf den jeweiligen Seiten findet sich ein entsprechendes script-Tag.
Das ist schon viel besser, aber da geht noch mehr:
Zunächst ist dieser Ansatz nur für Plattformen und Akteure praktikabel, die über IT-Ressourcen verfügen, um entsprechende Funktionalitäten bei sich einbauen zu können. Lehrende können dies nicht einfach auf ihrem privaten Blog oder ähnliches umsetzen. Zum anderen besteht immer noch ein Discovery Problem. Ich muss nach wie vor wissen, wo ich suchen muss. Ich muss die Sitemaps kennen, sonst finde ich nichts. Statt eines Ansatzes, bei dem Akteure eigenständig mitteilen können, dass sie neuen Content haben (Push-Ansatz), verfolgen wir derzeit einen Ansatz, bei dem jede Plattform für sich Content im Pull-Verfahren akquiriert. Dies führt an vielen Stellen zu Doppelarbeiten, ist ineffizient (mehrere Personen bauen genau die gleichen Crawler, aber halt immer für ihre Plattform) und schliesst vor allem kleine Akteure aus (lohnt es sich einen Crawler zu programmieren, wenn die Webseite "nur" 50 Materialien bereitstellt?).
Anstatt erschlossene Daten zu teilen, arbeiten die Plattformen für sich oder stellen es höchstens wieder hinter eigenen (offenen oder geschlossenen) Schnittstellen bereit. Das ist wohl nicht das, was wir uns unter einer offenen und kollaborativen Gemeinschaft vorstellen, oder?
Bei der Suche stehen wir vor ähnlichen Herausforderungen, wie bereits oben geschildert. Obwohl verschiedene OER-Aggregatoren in Form von Repositorien oder Referatorien bereits viele der "kleineren" Plattformen indexieren und somit eine übergreifende Suche anbieten, ist es nicht möglich, diese Aggregatoren gemeinsam zu durchsuchen. Dies führt im Endeffekt dazu, dass die User wieder verschiedene Plattformen ansteuern müssen, wenn sie den gesamten OER-Fundus durchsuchen wollen.
- An vielen Stellen wird Content doppelt erschlossen, aber immer für die eigene Plattform
- Es gibt keinen geteilten Datenraum, in den Akteure Content "pushen" können
- Es gibt keine plattformübergreifenden Suchmöglichkeiten
Plattformübergreifende Kollaboration
Das wäre schön, oder? Mir ist schleierhaft, wie #OEP (Open Educational Practices, genaue Definition durch die Community steht noch aus) ohne funktionieren soll. Aber es gibt meines Wissens nach nicht mal Ansätze, wie das technisch umgesetzt werden soll (oder doch? let me hear).
Ein Szenario für solche plattformübergreifende Kollaboration könnte Qualitätssicherung sein. Gesetzt, dass sich zwei Plattformen / Communities auf etwas verständigt haben, dass sie als "Qualität" bezeichnen, wie aber dieses Gütesiegel nun an den Content bringen?
Plattform A: Na, dann kommt doch alle zu uns. Hier können wir das machen und dann hängt auch ein schönes Badge an den Materialien.
Plattform B: Ja, aber dann hängt es ja nicht an unseren Materialien. Außerdem wollen/müssen wir bei uns arbeiten, weil welche Existenzberechtigung hat denn meine Plattform noch, wenn wir alles bei dir machen?
- Obwohl nun #OEP in aller Munde sind, gibt es keine technischen Ansätze, wie (plattformübergreifende) Kollaboration technisch abgebildet werden kann
KI-Services
Was ist heute schon komplett ohne das Thema KI zu erwähnen? Mindestens für den nächsten Förderantrag muss auch irgendetwas mit KI gemacht werden...
Verschiedene Projekte erarbeiten hilfreiche und beeindruckende KI-Services. Beispielsweise, um die Annotation von Content mit Metadaten zu erleichtern, Metadaten automatisch hinzuzufügen, Content zu bestimmten Themen zu finden oder (halb-)automatisch zu Sammlungen hinzuzufügen. Aber (vielleicht habt ihr es schon erraten): Funktioniert halt nur auf der eigenen Plattform. Vermutlich, weil die Services nah am plattformeigenen Datenmodell entwickelt werden. Und da die Daten dieses Silo nicht verlassen, passt das schon. Das führt dazu, dass an mehreren Stellen die gleichen Services doppelt entwickelt werden.
- KI-Services funktionieren oft nur auf der Plattform für die sie entwickelt werden
Zusammenfassung der Probleme
Wir machen übrigens vieles schon sehr gut (Einsatz des AMB, Offene Bidungsmaterialien, wir haben eine großartige Community) und jetzt müssen wir halt weiter gehen.
(Die OER-Metadatengruppe, die das Allgemeine Metadatenprofil für Bildungsressourcen (AMB) entwickelt hat, bekommt für ihre Arbeit keine direkte Förderung. Gleichzeitig ist sie eine zentrale Anlaufstelle für alle, die mit Metadaten in offenen Bildungsinfrastukturen hantieren und das Metadatenprofil ist eines der wenigen Applikationsprofile, das öffentlich einsehbar, gut dokumentiert ist und Validierungsmöglichkeiten bietet.)
Betrachten wir die gesamten Plattformen und die beschriebenen Herausforderungen aus der Vogelperspektive, so lassen sich drei ineinander verschränkte Kernbestandteile unterscheiden, die helfen, die beschriebenen Probleme besser zu verstehen:
- User
- Service
- Daten
User: Auf (fast) allen Plattformen agieren User. Sie laden Material hoch, annotieren mit Metadaten, sind in einer Community, suchen Content usw. Egal, ob sie sich einloggen können/müssen, irgendetwas bieten wir unseren Usern an, damit sie daraus hoffentlich Mehrwerte ziehen
Service: Das ist dieses irgendetwas. Die "Webseite", die Oberfläche, das, wo der User klicken und etwas tun kann. Es ist das, was den Daten oft eine "visuelle" Form gibt. Der Service ist der Mittler, das Interface zwischen User und Daten. Mithilfe des Services lassen sich Daten erzeugen, verändern oder entfernen (Es gibt natürlich auch viele nicht-visuelle Services, die Interaktion mit Daten ermöglichen, aber für die meisten normalen Menschen, gibt es irgendwo was zu klicken).
Daten: Die Informationen in strukturierter maschinenlesbarer Form, die dem User in gerenderter Form durch einen Service Mehrwerte bieten können. Ungerenderte Daten können wir schwieirg erfassen (wir sind ja nicht Neo). Das können entweder die Metadaten zu Bildungmaterialien sein, die Materialien selbst, Profilinformationen, Materialsammlungen o.ä.

Meines Erachtens nach haben viele der oben beschriebenen Herausforderungen ihren Ursprung darin, dass die drei Kernbestandteile User, Service, Daten ungünstig miteinander verbunden wurden. Was kein Vorwurf sein soll, denn das ist genau die Art und Weise, wie die letzten Jahre (Jahrzehnte?) Plattformen immer gebaut wurden:
- User, Service und Daten werden in einer Plattform gebündelt
Das heisst durch meinen Service agieren die User mit den Daten und ich kann sicherstellen, dass in meiner kleinen Welt alles gut miteinander funktioniert. Sinnvoll, wenn ich Microsoft, Facebook, X oder ähnliches bin, weil mein Geschäftsmodell genau darin liegt: User einschließen (lock-in), ihnen die Hohheit über ihren Content nehmen (oder kannst du deine Facebook Posts zu X migrieren?) und nach Möglichkeit nicht wieder rauslassen.
Aber unsere Projekte sind öffentlich. Das sind nicht die Mechanismen, die wir replizieren sollten. Also was nun?
Bildungsinfrasstrukturen auf Basis des Nostr-Protokolls
Nostr
Eine pseudonyme Person mit dem Namen "fiatjaf" hat 2019 ein Konzept für ein Social Media Protokoll "Nostr - Notes and Other Stuff Transmitted By Relays" wie folgt beschrieben:
It does not rely on any trusted central server, hence it is resilient, it is based on cryptographic keys and signatures, so it is tamperproof, it does not rely on P2P techniques, therefore it works.
Fiatjaf, 2019
Die Kernbestandsteile des Protokolls bestehen aus:
- JSON -> Datenformat
- SHA256 & Schnorr -> Kryptographie
- Websocket -> Datenaustausch
Und funktionieren tut es so:
User besitzen ein "Schlüsselpaar": einen privaten Schlüssel (den behälst du für dich, nur für dich) und einen öffentlichen Schlüssel, den kannst du herumzeigen, das ist deine öffentliche Identität. Damit sagst du anderen Usern: Hier schau mal, das bin ich. Die beiden Schlüssel hängen dabei auf eine "magische" (kryptografische) Weise zusammen: Der öffentliche Schlüssel lässt sich aus dem privaten Schlüssel generieren, jedoch nicht andersherum. D.h. falls du deinen öffentlichen Schlüssel verlierst: Kein Problem, der lässt sich immer wieder herstellen. Wenn du deinen privaten Schlüssel verlierst: Pech gehabt, es ist faktisch unmöglich, diesen wieder herzustellen.
Die Schlüsselmagie geht jedoch noch weiter: Du kannst mit deinem privaten Schlüssel "Nachrichten" signieren, also wie unterschreiben. Diese Unterschrift, die du mit Hilfe des privaten Schlüssels erstellst, hat eine magische Eigenschaft: Jeder kann mithilfe der Signatur und deinem öffentlichen* Schlüssel nachprüfen, dass nur die Person, die auch den privaten Schlüssel zu diesem öffentlichen Schlüssel besitzt, diese Nachricht unterschrieben haben kann. Magisch, richtig? Verstehst du nicht komplett? Nicht schlimm, du benutzt es bereits vermutlich, ohne dass du es merkst. Das ist keine fancy neue Technologie, sondern gut abgehangen und breit im Einsatz.
Merke: User besitzen ein Schlüsselpaar und können damit Nachrichten signieren.
Dann gibt es noch die Services. Services funktionieren im Grunde wie bereits oben beschrieben. Durch sie interagieren die User mit Daten. Aber bei Nostr ist es ein kleines bisschen anders als sonst, denn: Die Daten "leben" nicht in den Services. Aber wo dann?
Wenn ein User einen Datensatz erstellt, verändert oder entfernen möchte, wird dieses "Event" (so nennen wir das bei Nostr) mit deinem privaten Schlüssel signiert (damit ist für alle klar, nur du kannst das gemacht haben) und dann mehrere "Relays" gesendet. Das sind die Orte, wo die Daten gehalten werden. Wenn ein User sich in einen Service einloggt, dann holt sich der Service die Daten, die er braucht von diesen Relays. User, Service und Daten sind also entkoppelt. Der User könnte zu einem anderen Service wechseln und sich dieseleben Daten von den Relays holen. Keine Lock-In Möglichkeiten.
Merke: User, Service und Daten sind entkoppelt.
Zuletzt gibt es noch die Relays. Relays sind Orte. Es sind die Orte, zu denen die Events, also die Daten der User, ihre Interaktionen, gesendet und von denen sie angefragt werden. Sie sind sowas wie das Backend von Nostr, allerdings tun sie nicht viel mehr als das: Events annehmen, Events verteilen. Je nach Konfiguration dürfen nur bestimmte User auf ein Relay schreiben oder davon lesen.
Das Protokoll ist von seinem Grunddesign auf Offenheit und Interoperabilität ausgelegt. Keine Registrierung ist nötig, sondern nur Schlüsselpaare. Durch kryptografische Verfahren kann dennoch die Authentizitität eines Events sichergestellt werden, da nur die Inhaberin des jeweiligen Schlüsselpaares dieses Event so erstellen konnte. Die Relays sorgen dafür die Daten an die gewünschten Stellen zu bringen und da wir mehr als nur eines benutzen, haben wir eine gewisse Ausfallsicherheit. Da die Daten nur aus signierten JSON-Schnipseln bestehen, können wir sie leicht an einen anderen Ort kopieren, im Falle eines Ausfalls. Durch die Signaturen ist wiederum sichergestellt, dass zwischendurch keine Veränderungen an den Daten vorgenommen wurden.
Beispiel: Ein Nostr Event
Hier ein kleiner technischer Exkurs, der beschreibt, wie Nostr Events strukturiert sind. Falls dich die technischen Details nicht so interessieren, überspringe diesen Abschnitt ruhig.
Jedes Nostr Event besitzt die gleiche Grundstruktur mit den Attributen:
id: Der Hash des Eventspubkey: Der Pubkey des Urhebers des Eventscreated_at: Der Zeitstempel des Eventskind: Der Typ des Eventstags: Zusätzliche Metadaten für das Event können in diesem Array hinterlegt werdencontent: Der textuelle Inhalt eines Eventssig: Die Signatur des Events, um die Integrität der Daten zu überprüfen
json { "id": <32-bytes lowercase hex-encoded sha256 of the serialized event data>, "pubkey": <32-bytes lowercase hex-encoded public key of the event creator>, "created_at": <unix timestamp in seconds>, "kind": <integer between 0 and 65535>, "tags": [ [<arbitrary string>...], // ... ], "content": <arbitrary string>, "sig": <64-bytes lowercase hex of the signature of the sha256 hash of the serialized event data, which is the same as the "id" field> }Die verwendeten Eventtypen sowie die existierenden Spezifikationen lassen sich unter https://github.com/nostr-protocol/nips/ einsehen.
Wichtig ist auch: Du kannst einfach anfangen, Anwendungen zu entwickeln. Die Relays werden alle Events akzeptieren, die dem o.g. Schema folgen. Du musst also niemanden um Erlaubnis fragen oder warten, bis deine Spezifikation akzeptiert und hinzugefügt wurde.
You can just build things.
Exkurs: Nostr für Binärdaten - Blossom
Ja, aber... das ist doch nur für textbasierte Daten geeignet? Was ist denn mit den Binärdaten (Bilder, Videos, PDFs, etc)
Diese Daten sind oft recht groß und es wurde sich auf das Best-Practice geeignet, diese Daten nicht auf Relays abzulegen, sondern einen besser geeigneten Publikationsmechanismus für diese Datentypen zu finden. Der Ansatz wird als "Blossom - Blobs stored simply on mediaservers" bezeichnet und ist recht unkompliziert.
Blossom Server (nichts anderes als simple Medienserver) nutzen Nostr Schlüsselpaare zur Verwaltung Identitäten und zum Signieren von Events. Die Blobs werden über ihren sha256 Hash identifiziert. Blossom definiert einige standardisierte Endpunkte, die beschreiben wie Medien hochgeladen werden können, wie sie konsumiert werden können usw.
Die Details, wie Authorisierung und die jeweiligen Endpunkte funktionieren, werden in der genannten Spezifikation beschrieben.
Nostr 🤝 Öffentliche Bildungsinfrastrukturen
Wie könnten Herausforderungen gelöst werden, wenn wir Nostr als Basis für die öffentliche Bildungsinfrastruktur einsetzen?
Material-Upload
- Es ist nicht einfach möglich OER bereitzustellen, sodass es auch auf verschiedenen Plattformen gefunden werden kann.
Mit Nostr als Basis-Infrastruktur würden die Metadaten und die Binärdaten nicht an den Service gekoppelt sein, von dem aus sie bereitgestellt wurden. Binärdaten können auf sogenannten Blossom-Servern gehostet werden. Metadaten, Kommentare und weitere textbasierte Daten werden über die Relay-Infrastruktur verteilt. Da Daten und Service entkoppelt sind, können die OER Materialien von verschiedenen Anwendungen aus konsumiert werden.
Kuration
- Es gibt keine interoperablen Sammlungen
- Metadaten-Annotation ist zentralisiert
- User können keine eigenen Metadaten hinzufügen
Sammlungen sind per se interoperabel. Auf Protokollebene ist definiert, wie Listen funktionieren. Die Annotation mit Metadaten ist an keiner Stelle zentralisiert. Das Versprechen der RDF-Community "Anyone can say anything about any topic" wird hier verwirklicht. Ich muss mir ja nicht alles anhören. Vielleicht konsumiere ich nur Metadaten-Events bestimmter Redaktionen oder User. Vielleicht nur diejenigen mit einer Nähe zu meinem sozialen Graphen. Jedenfalls gibt es die Möglichkeit für alle User entsprechende Metadaten bereit zu stellen.
Crawling, Indexierung und Suche * An vielen Stellen wird Content doppelt erschlossen, aber immer für die eigene Plattform * Es gibt keinen geteilten Datenraum, in den Akteure Content "pushen" können * Es gibt keine plattformübergreifenden Suchmöglichkeiten
Keine Doppelerschließungen mehr. Wenn ein User im Netzwerk ein Metadatenevent veröffentlicht hat, ist es für alle konsumierbar. Der Datenraum ist per se geteilt. Plattformübergreifende Suche wird durch die Kombination aus Relays und NIPs ermöglicht. In den NIPs können spezielle Query-Formate für die jeweiligen NIPs definiert werden. Relays können anzeigen, welche NIPs sie untersützten. Eine plattformübergreifende Suche ist im Nostr eine relay-übergreifende Suche.
Plattformübergreifende Kollaboration
- Obwohl nun #OEP in aller Munde sind, gibt es keine technischen Ansätze, wie (plattformübergreifende) Kollaboration technisch abgebildet werden kann
Nostr ist der technische Ansatz.
KI-Services
- KI-Services funktionieren oft nur auf der Plattform für die sie entwickelt werden
Es gibt im Nostr das Konzept der Data Vending Machines (s. auch data-vending-machines.org). Statt also einfach nur eine API zu bauen (was auch schon sehr schön ist, wenn sie offen zugänglich ist), könnten diese Services auch als Akteure im Nostr Netzwerk fungieren und Jobs annehmen und ausführen. Die Art der Jobs kann in einer Spezifikation beschrieben werden, sodass die Funktionsweise für alle interessierten Teilnehmer im Netzwerk einfach nachzuvollziehen ist.
Die Services könnten sogar monetarisiert werden, sodass sich hier auch Möglichkeiten böten, Geschäftsmodelle zu entwickeln.
Fazit
Die Open Education Community ist großartig. Es sind einzigartige und unglaublich engagierte Menschen, die sich dem hehren Ziel "Zugängliche Bildung für Alle" -> "Offene Bildung" verschrieben haben. Wir verwenden Creative Commons Lizenzen -> Commons -> Gemeingüter. Es ist okay, dass viele Projekte von Sponsoren und Förderungen abhängig sind. Was wir machen, ist im Sinne eines Gemeingutes: Öffentliche Bildung für alle. Also zahlen wir als Gemeinschaft alle dafür.
Was nicht okay ist: Dass das, wofür wir alle gezahlt haben, nach kurzer Zeit nicht mehr auffindbar ist. Dass es eingeschlossen wird. In öffentlich finanzierten Datensilos. Es muss für alle auch langfristig verfügbar sein. Sonst ist es nicht zugänglich, nicht offen. Dann ist das O in OER nur ein Label und Marketing, um für eine ABM-Maßnahme 3 Jahre Geld zu bekommen. Denn nichts anderes ist Content-Entwicklung, wenn der Content nach drei Jahren weggeschmissen wird.
Und dasselbe gilt für OEP. Offene Lernpraktiken, sind auch nur eine Phrase, wenn wir die passende technische Infrastruktur nicht mitdenken, die wirkliche Offenheit und Kollaboration und damit die Umsetzung offener Lernpraktiken ermöglicht.
Und wenn wir uns jetzt nicht Gedanken darüber machen, die Infrastruktur für offenes Lernen anzupassen, dann werden wir vermutlich in einigen Jahren sehen können, was bei politischen Umorientierungen noch davon übrig bleiben wird. Wenn die Fördertöpfe komplett gestrichen werden, was bleibt dann übrig von dem investierten Geld?
Wir brauchen Lösungen, die engagierte Communities weiter betreiben können und denen kein Kopf abgeschlagen werden kann, ohne dass wir zwei neue daneben setzen könnten.
Wir müssen uns jetzt Gedanken darüber machen.
Wie offen will öffentliche Bildungsinfrastruktur sein?
-
 @ e2c72a5a:bfacb2ee
2025-06-05 17:00:01
@ e2c72a5a:bfacb2ee
2025-06-05 17:00:01Forget Lambos, think real estate tokens.
A European fund just dropped $3.4 million on tokenized real estate, marking the first time big money directly bought retail available tokens. This isn't just about crypto hype; it's about institutions embracing regulated crypto assets. Real World Assets (RWAs) are booming, up 260% this year, fueled by clearer US crypto rules. This surge pushes the tokenization sector past $23 billion.
Is this the start of crypto's mainstream moment?
-
 @ e2c72a5a:bfacb2ee
2025-06-05 16:54:43
@ e2c72a5a:bfacb2ee
2025-06-05 16:54:43Think your crypto is FDIC insured like your bank account? Big mistake. Crypto's wild west demands you be your own bank and security guard.
Crypto trading involves buying, selling, and exchanging digital currencies like Bitcoin or Ethereum, aiming to profit from price fluctuations. Security is paramount. Understand basic concepts like wallets (digital storage for your crypto), private keys (passwords to access your crypto), and blockchain (the technology that records all transactions).
Real world applications include using crypto for online purchases, international money transfers, and decentralized finance (DeFi) services like lending and borrowing. Current trends include the rise of DeFi, NFTs (non-fungible tokens), and increasing institutional investment.
Best practices? Use strong, unique passwords, enable two factor authentication (2FA) on all accounts, and store most of your crypto in cold wallets (offline storage) to protect against hacking. Be wary of phishing scams and fake websites. Never share your private keys or seed phrases.
Misconceptions? Crypto is not anonymous, transactions are not easily reversible, and past performance is not indicative of future results. Also, remember that regulations are evolving, so stay informed.
With crypto hacks on the rise, are you truly ready to secure your digital fortune, or are you leaving the door open for the next billion dollar heist?
-
 @ e2c72a5a:bfacb2ee
2025-06-05 16:50:08
@ e2c72a5a:bfacb2ee
2025-06-05 16:50:08Think crypto is just magic internet money? Think again.
Tokenomics is the secret sauce that makes or breaks a crypto project. It is the study of how tokens are created, distributed, and used within a blockchain ecosystem. Imagine it as the economic policy of a digital nation, dictating everything from supply and demand to user incentives.
Key features include supply caps, distribution models, utility, and burn mechanisms. A well designed token economy incentivizes user behavior, secures the network, and fosters long term growth. Poor tokenomics? It can lead to manipulation and project failure.
Zero Knowledge Proofs are like showing you know a password without revealing the password itself. This tech allows for private and secure transactions, verifying data without exposing the data itself. Think of voting systems where your vote stays secret, or supply chains where product details are confirmed without revealing the supplier.
Want to dive deeper into the economics of crypto? What project has the most interesting tokenomics you have seen?
-
 @ ca76c778:e784c54b
2025-06-04 19:45:11
@ ca76c778:e784c54b
2025-06-04 19:45:11A few days ago I remembered video by Antonio Stappaerts(Artwod) on Youtube. And I thought to myself I want to be really good at drawing hands.\ In the video he explains something that, in my opinion, applies when learning just about anything.
If you've heard of the Dunning-Kruger effect then you know the first part.\ If you haven't, one begins learning something and on top of the first peak thinks oneself to be almost a master. And then one learns a little bit more and realizes how little skill one actually has.
 \
Now, what is really interesting is this. He points out that the second slope is made up of many smaller Dunning-Kruger effects. For example the effect will apply when learning: the basic shape of the figure, how to pose the figure, how draw the hands, the hair etc.
\
Now, what is really interesting is this. He points out that the second slope is made up of many smaller Dunning-Kruger effects. For example the effect will apply when learning: the basic shape of the figure, how to pose the figure, how draw the hands, the hair etc.So the way to climb the second hill is to understand and practice these smaller skills. And not just once or twice. You want to reach close to the second peak of each of the smaller skills.
And with that in mind I search for a good tutorial about drawing hands and got down to it(for the third time).
Step one was to learn pose and gesture using a grid shape.
https://cdn.satellite.earth/f55a9d1ef2fd687a9dce5ceee5e05a1b666c436509e264ddbac4d260b99e882a.jpg
https://cdn.satellite.earth/1b5524635c20ee4869f4860c982deea469cb87be7ad7b404e1777497b5a4fbd4.jpg
https://cdn.satellite.earth/35652251243ffd8c495b855c319d27da0c193ff2e951591f0a9f1b35aad39b29.jpg
https://cdn.satellite.earth/68f55979d102b4ebe55177842c6d9ab2ab30b95f926441429d977b47fae925c3.jpg
Step two. Practice the basic forms for the palm and fingers.\ I got carried away and drew some hands.
https://cdn.satellite.earth/48b400f72e35d078368149f00182cb58e606ddd16f6db4e7789c1431c28d44a0.jpg
Step three. learn the measurements.
https://cdn.satellite.earth/75c9b82da90ef50d17f698dd7b1eadc223b74a019a702a4617ed7d321646a87c.jpg
Step four. Understand the fingers.
https://cdn.satellite.earth/e33f9f3f9217bf5e3e206e96dfe764eba09b9fb3c10b450bb9c8a4075e3c1ec8.jpg
Step five. Learn about the thumb and put it all together. Drawing from reference and imagination.
https://cdn.satellite.earth/b2dd9c1cc1045dde021272199818b0db331e71a603c5900122aa850eb2d4148a.jpg
https://cdn.satellite.earth/8f5647ae9e148ad6217c106b5b69cf231384475e0a0eedf210bd149f75ade0b7.jpg
-
 @ a74cf7d3:37b9b82e
2025-06-05 17:03:04
@ a74cf7d3:37b9b82e
2025-06-05 17:03:04Lava is the most secure way to borrow against your bitcoin. Lava Loans allow you to borrow dollars using your bitcoin as collateral, all without giving up self-custody. No need to wait days, sign paperwork, bridge your bitcoin, or trust third-party custodians to take out a loan. All you have to do is set the terms of your loan within your Lava Vault, and you can get your loan capital within seconds.
Unlike other bitcoin-backed lending options, Lava is entirely self-custodial. You control your own keys and never have to transfer your bitcoin to a third party. Historically, most bitcoin-backed lending solutions required users to trust custodians with their bitcoin, exposing them to hacks, rehypothecation risk, insolvency, and seizures. This resulted in more than $24B in user funds lost in 2022 alone. Lending protocols on other chains like Ethereum or Solana require users to bridge their bitcoin, introducing additional custodial, bridge, smart contract, and platform risks. Both options are clunky, risky, and slow.
Lava Loans introduces a better model. We’ve built a borrowing protocol that works entirely on native bitcoin. Taking out a loan on Lava takes seconds, doesn't require paperwork, and allows you to maintain self-custody. Lava is the best option for simple, low-cost, and safe bitcoin-backed loans.
In this article we’ll dive into the key features of Lava Loans, how it is different from other borrowing options on the market, and explain how it works at a technical level.
Key Features of Lava
-
Instant loans: No paperwork. Just answer 2 questions and get your loan within seconds.
-
Low cost: We minimize costs by reducing loan risk, allowing us to offer the lowest rates on the market. All fees are made transparent at the start.
-
Flexible amounts: Borrow exactly what you need.
-
No Custodial Risk: Your BTC never leaves your control. There’s no risk of hacks, seizure, or rehypothecation. You can verify this yourself on-chain. Lava is the only loan product where you can independently verify—on-chain and in real time—that your bitcoin is not being rehypothecated.
-
No Loan Initiation Risk: Using atomic swaps, your collateral only moves if your loan capital is already secured.
-
No Repayment Risk: Repay your loan and your BTC is automatically returned, guaranteed by cryptography.
-
Reduced Liquidation Risk: You choose your own blinded, off-chain price source, minimizing the chance of unfair liquidation.
-
Bug-Minimized: Lava uses formally verified smart contracts on bitcoin (Discreet Log Contracts), meaning all contract outcomes are known and signed ahead of time. Execution is private and secure.
How It Works
The Lava Loans Protocol is built on top of bitcoin-native smart contracts, called Discreet Log Contracts (DLCs). DLCs enable conditional (oracle-based) contracts on bitcoin, meaning they can execute transactions based on pre-specified and approved conditions. Lava Loans are executed via custom DLCs that allow the borrower and lender to agree to the terms of a loan, enter into a contract based on those terms, and have the contract enforce the terms on-chain— all without requiring a third-party custodian.
DLCs allow for a trust-minimized borrowing experience, and they avoid many of the risks inherent with smart contracts on other platforms like Ethereum. DLCs operate on Bitcoin itself— you don’t need to move your coins to another chain or layer. They also mitigate bug risk because they are formally verified, meaning the output conditions of the contract are known from the beginning. This helps to avoid the exploits commonly seen in Ethereum. Because the contracts use off-chain oracles, they aren't susceptible to oracle manipulation by miners. Not only that, but these contracts are private, customizable (choose your own oracle), and scalable (minimal on-chain cost because execution happens off-chain).
Lava Loans are on-chain contracts between borrowers and lenders. The borrower and the lender agree on a loan amount (in USD), a collateral amount (in BTC), the loan duration, the interest rate, the loan-to-value (LTV) ratio at which liquidation happens, and a data feed (oracle) that will provide the Bitcoin price. When the contract is initialized, the collateral is locked and the loan capital is transferred to the borrower. The oracle feeds the price of Bitcoin into the contract on a continuous basis, and the contract executes according to its pre-defined parameters. As long as the borrower maintains a healthy LTV and repays their loan, their collateral is automatically returned to them upon completion.
Each Lava Loan goes through three phases:
Phase 1: Loan Initiation
- The loan is initialized via an atomic swap; the bitcoin collateral is locked in the smart contract and the loan capital is transferred from the lender to the borrower. Because this is done via an atomic swap, the borrower and lender do not have to trust one another or use an escrow. The collateral moves into the smart contract, and the loan capital is automatically sent to the borrower.
Phase 2: Active Loan
-
Once the atomic swap is complete, the loan is active. The bitcoin collateral remains locked in the smart contract, and the borrower has access to their loan capital.
-
While the loan is active, the oracle feeds the bitcoin price into the contract on an ongoing basis. This allows the contract to monitor the LTV.
Phase 3: Loan Termination
Once the loan is active, it can terminated in one of the following ways:
-
Repaid: If the borrower repays the loan, the collateral is released to the borrower atomically.
-
Liquidated: If the loan value reaches a pre-determined LTV or the borrower misses a payment, the collateral is immediately released to the lender for liquidation.
-
Expired: If the borrower does not repay the loan before the loan term ends, some of the collateral, equivalent to principal plus interest, is released to the lender, and the rest is sent to the borrower.
-
Fail-Safe: In rare scenarios where the loan process cannot be completed as expected due to unresponsive oracles, the protocol has built-in fail-safe mechanisms. These mechanisms ensure that the collateral is not lost.
As you can see, all of the loan terms and conditions are built into the smart contract. The borrower and lender agree on the terms, enter into the loan, and then the contract executes the pre-specified and approved transactions based on either the actions taken by the borrow/lender, or the price changes in BTC. As a user, you can verify at any point that your collateral sits on-chain, is locked in the contract, and isn’t being used or rehypothecated in any way.
Security
Lava Loans are designed to be the most secure option for Bitcoiners who want to borrow against their holdings. Lava’s approach is trust-minimized, bug-minimized, and verifiable for users.
Trust-Minimized
-
Traditional platforms expose you to bridge, custodian, or bank risk. Lava lets you borrow against native-BTC directly in your vault. This means there can’t be rehypothecation, funds lost in custodial hacks, or asset confiscation.
-
While other platforms require blind trust during loan initiation, Lava uses atomic swaps to ensure your BTC collateral only moves to the escrowed smart contract once the loan is in your hands.
-
The uncertainty of receiving collateral post-repayment is a concern with many platforms. Lava uses cryptographic guarantees to ensure that once you fulfill your repayment, your BTC is promptly returned.
-
You don’t have to trust a lender who can liquidate your BTC unjustly. With Lava, you choose your off-chain, blinded oracles per loan to provide price data, drastically reducing risks from malicious entities.
Bug-Minimized
-
Lava’s bitcoin smart contract is formally-verified, meaning the output conditions to the contract are known ahead of time, minimizing technical risk. DLCs, the underlying technology Lava uses, use pre-signed, encrypted transactions to specify the output conditions to a contract ahead of time. Since all the output conditions to the contract are specified ahead of time, and then encrypted using adaptor signatures, the output conditions are known (money can only move to borrower/lender).
-
Lava’s contracts have been audited by the best auditors in the industry, Antoine Riard from thelab31 and Conduition, as well as the core contributors to the cryptography behind DLCs.
Verifiable
-
Lava is the only loan product where you can independently verify—on-chain and in real time—that your bitcoin is not being rehypothecated. When you borrow using Lava, you have cryptographic proof, not just legal or reputational assurances, that your collateral is secure.
-
Lava’s oracle implementation is open-source.
-
Lava’s oracles make daily attestations and calculate a median price across various price feeds to avoid flash crash and unreliable margin call risk.
How Lava Compares

Loan Payments + Fees
Users who take out a Lava Loan pay a one-time origination fee (currently 2%) to open a loan, and each loan has a determined, fixed interest rate for the duration of the loan. Interest rates depend on the length of the loan, but they currently start at 5% annually. Users can also extend their loan by paying an extension fee (currently 2%) at the time that the loan is extended.
Loans that are longer than one month in duration require users to make monthly payments on their loans. Because the terms of Lava Loans are set programmatically in the smart contract, users must make their monthly payments on time in order to avoid being liquidated. You can make your monthly payments using digital dollars (either those held in your Lava Vault, or by depositing USDC into the vault) or via bank transfer. Bank transfers may take several days to clear, so it’s important to plan ahead in order to make the payments on time. Lava offers notifications in advance of payment deadlines in order to allow you sufficient time to plan and make payments.
FAQ
What are oracles?
Oracles are independent data feeds that attest to the price of Bitcoin and feed that price into the contract. At Lava, we’ve built Sibyls, an open-source oracle implementation for bitcoin. Users can choose their own oracles, and oracles have zero knowledge about the contracts they influence. In the case of the Lava Loans Protocol, oracles also make off-chain attestations, and in doing so, this helps us avoid the increased fees and miner manipulation that comes from on-chain oracles. You can learn more about our oracles here.
Why does Lava use digital dollars?
To ensure a fast, trust-minimized loan, Lava uses smart contracts that require HTLC compatibility. Fiat doesn’t support this, so we use digital dollars (like USDC on Solana) — which you can instantly withdraw to your bank account.
What are bitcoin smart contracts?
Bitcoin smart contracts (also known as discreet log contracts) enable conditional (oracle-based) contracts on bitcoin. The way it works is that each party to a contract creates and shares encrypted signatures for each output condition to the contract. Each counterparty has confidence they can decrypt the encrypted signatures and use them correctly at the right time because they can verify the encryption: verify when they can decrypt the signatures and that the signatures are valid.
Bitcoin smart contracts are a better way to do smart contracts because they are secure, private, customizable, and scalable. They mitigate bug risk because they are formally verified, meaning the output conditions of the contract are known from the beginning. This helps avoid exploits you constantly see in Ethereum. Since these contracts use off-chain oracles, they aren't susceptible to oracle manipulation by miners. Not only that, but these contracts are private, customizable (choose your own oracle), and scalable (minimal on-chain cost because execution happens off-chain).
These contracts are zero knowledge in that the blockchain has zero knowledge about the contract, the oracles have zero knowledge about the contract, and the counterparty can verify the encryption without needing the decrypted material.
Where can I learn more?
If you want to learn more about the Lava Loans Protocol, check out the loans paper here: https://github.com/lava-xyz/loans-paper/tree/main
Ready to borrow? Download the Lava Vault on iOS or Android and take out your first bitcoin-secured loan in seconds.
-
-
 @ 2cde0e02:180a96b9
2025-06-05 15:13:03
@ 2cde0e02:180a96b9
2025-06-05 15:13:03pen & ink; monochromized
Magdalena Carmen Frida Kahlo y Calderón[a] (Spanish pronunciation: [ˈfɾiða ˈkalo]; 6 July 1907 – 13 July 1954[1]) was a Mexican painter known for her many portraits, self-portraits, and works inspired by the nature and artifacts of Mexico. Inspired by the country's popular culture, she employed a naïve folk art style to explore questions of identity, postcolonialism, gender, class, and race in Mexican society.[2] Her paintings often had strong autobiographical elements and mixed realism with fantasy. In addition to belonging to the post-revolutionary Mexicayotl movement, which sought to define a Mexican identity, Kahlo has been described as a surrealist or magical realist.[3] She is also known for painting about her experience of chronic pain.[4]
https://stacker.news/items/997980
-
 @ e2c72a5a:bfacb2ee
2025-06-05 16:46:19
@ e2c72a5a:bfacb2ee
2025-06-05 16:46:19Think proving you're over 21 without showing your ID is impossible? Zero Knowledge Proofs make it real.
Zero Knowledge Proofs let you prove something is true without revealing the information itself. Imagine proving you know a password without saying it. It's like magic, but it's math.
They're used in crypto for private transactions, secure voting, and faster blockchains. Zcash and Aztec use them to hide transaction details. StarkWare uses them to make Ethereum faster.
But here's the twist: zk STARKs don't need a trusted setup, unlike zk SNARKs. This makes them more secure and decentralized.
Misconception alert: ZKPs aren't just for privacy. They also boost scalability and interoperability.
Want to dive deeper into this mind bending tech? What other secrets can ZKPs unlock?
-
 @ a5ee4475:2ca75401
2025-06-04 18:11:52
@ a5ee4475:2ca75401
2025-06-04 18:11:52clients #link #list #english #article #finalversion #descentralismo
*These clients are generally applications on the Nostr network that allow you to use the same account, regardless of the app used, keeping your messages and profile intact.
**However, you may need to meet certain requirements regarding access and account NIP for some clients, so that you can access them securely and use their features correctly.
CLIENTS
Twitter like
- Nostrmo - [source] 🌐💻(🐧🪟🍎)🍎🤖(on zapstore)
- Coracle - Super App [source] 🌐🤖(on zapstore)
- Amethyst - Super App with note edit, delete and other stuff with Tor [source] 🤖(on zapstore)
- Primal - Social and wallet [source] 🌐🍎🤖(on zapstore)
- Iris - [source] 🌐🤖🍎
- Current - [source] 🤖🍎
- FreeFrom 🤖🍎
- Openvibe - Nostr and others (new Plebstr) [source] 🤖🍎
- Snort 🌐(🤖[early access]) [onion] [source]
- Damus 🍎 [source]
- Nos 🍎 [source]
- Nostur 🍎 [source]
- NostrBand 🌐 [info] [source]
- Yana [source] 🌐💻(🐧) 🍎🤖(on zapstore)
- Nostribe [on development] 🌐 [source]
- Lume 💻(🐧🪟🍎) [info] [source]
- Gossip - [source] 💻(🐧🪟🍎)
- noStrudel - Gamified Experience [onion] [info/source] 🌐
- [Nostrudel Next] - [onion]
- moStard - Nostrudel with Monero [onion] [info/source] 🌐
- Camelus - [source] 🤖 [early access]
Community
- CCNS - Community Curated Nostr Stuff [source]
- Nostr Kiwi [creator] 🌐
- Satellite [info] 🌐
- Flotilla - [source] 🌐🐧🤖(on zapstore)
- Chachi - [source] 🌐
- Futr - Coded in haskell [source] 🐧 (others soon)
- Soapbox - Comunnity server [info] [source] 🌐
- Ditto - Soapbox community server 🌐 [source] 🌐
- Cobrafuma - Nostr brazilian community on Ditto [info] 🌐
- Zapddit - Reddit like [source] 🌐
- Voyage (Reddit like) [on development] 🤖
Wiki
- Wikifreedia - Wiki Dark mode [source] 🌐
- Wikinostr - Wiki with tabs clear mode [source] 🌐
- Wikistr - Wiki clear mode [info] [source] 🌐
Search
- Keychat - Signal-like chat with AI and browser [source] 💻(🐧🪟🍎) - 📱(🍎🤖{on zapstore})
- Spring - Browser for Nostr apps and other sites [source] 🤖 (on zapstore)
- Advanced nostr search - Advanced note search by isolated terms related to a npub profile [source] 🌐
- Nos Today - Global note search by isolated terms [info] [source] 🌐
- Nostr Search Engine - API for Nostr clients [source]
- Ntrends - Trending notes and profiles 🌐
Website
- Nsite - Nostr Site [onion] [info] [source]
- Nsite Gateway - Nostr Site Gateway [source]
- Npub pro - Your site on Nostr [source]
App Store
ZapStore - Permitionless App Store [source] 🤖 💻(🐧🍎)
Video and Live Streaming
- Flare - Youtube like 🌐 [source]
- ZapStream - Lives, videos, shorts and zaps (NIP-53) [source] 🌐 🤖(lives only | Amber | on zapstore)
- StreamCat - [source code dont found]
- Shosho - Stream your camera [source] 🤖(on zapstore)
- Swae - Live streaming [source] (on development) ⏳
Post Aggregator - Kinostr - Nostr Cinema with #kinostr [english] [author] 🌐 - Stremstr - Nostr Cinema with #kinostr [english] [source] 🤖
Link Agreggator - Kinostr - #kinostr - Nostr Cinema Profile with links [English] - Equinox - Nostr Cinema Community with links [Portuguese]
Audio and Podcast Transmission
- Castr - Your npub as podcast feed [source]
- Nostr Nests - Audio Chats [source] 🌐
- Fountain - Podcast [source] 🤖🍎
- Corny Chat - Audio Chat [source] 🌐
Music
- Tidal - Music Streaming [source] [about] [info] 🤖🍎🌐
- Wavlake - Music Streaming [source] 🌐(🤖🍎 [early access])
- Tunestr - Musical Events [source] [about] 🌐
- Stemstr - Musical Colab (paid to post) [source] [about] 🌐
Images
- Lumina - Trending images and pictures [source] 🌐
- Pinstr - Pinterest like [source] 🌐
- Slidestr - DeviantArt like [source] 🌐
- Memestr - ifunny like [source] 🌐
Download and Upload
Documents, graphics and tables
- Mindstr - Mind maps [source] 🌐
- Docstr - Share Docs [info] [source] 🌐
- Formstr - Share Forms [info] 🌐
- Sheetstr - Share Spreadsheets [source] 🌐
- Slide Maker - Share slides 🌐 [Advice: Slide Maker https://zaplinks.lol/ site is down]
Health
- Sobrkey - Sobriety and mental health [source] 🌐
- Runstr - Running app [source] 🌐
- NosFabrica - Finding ways for your health data 🌐
- LazerEyes - Eye prescription by DM [source] 🌐
Forum
- OddBean - Hacker News like [info] [source] 🌐
- LowEnt - Forum [info] 🌐
- Swarmstr - Q&A / FAQ [info] 🌐
- Staker News - Hacker News like 🌐 [info]
Direct Messenges (DM)
- 0xchat 🤖🍎 [source]
- Nostr Chat 🌐🍎 [source]
- Blowater 🌐 [source]
- Anigma (new nostrgram) - Telegram based [on development] [source]
Reading
- Oracolo - A minimalist Nostr html blog [source]
- nRSS - Nostr RSS reader 🌐
- Highlighter - Insights with a highlighted read [info] 🌐
- Zephyr - Calming to Read [info] 🌐
- Flycat - Clean and Healthy Feed [info] 🌐
- Nosta - Check Profiles [on development] [info] 🌐
- Alexandria - e-Reader and Nostr Knowledge Base (NKB) [source] 🌐
Writing
- Habla - Blog [info] 🌐
- Blogstack - Blog [info]🌐
- YakiHonne - Articles and News [info] 🌐🍎🤖(on zapstore)
Lists
- Following - Users list [source] 🌐
- Nostr Unfollower - Nostr Unfollower
- Listr - Lists [source] 🌐
- Nostr potatoes - Movies List [source] 💻(numpy)
Market and Jobs
- Shopstr - Buy and Sell [onion] [source] 🌐
- Nostr Market - Buy and Sell 🌐
- Plebeian Market - Buy and Sell [source] 🌐
- Ostrich Work - Jobs [source] 🌐
- Nostrocket - Jobs [source] 🌐
Data Vending Machines - DVM (NIP90)
(Data-processing tools)
Games
- Chesstr - Chess 🌐 [source]
- Jestr - Chess [source] 🌐
- Snakestr - Snake game [source] 🌐
- Snakes on a Relay - Multiplayer Snake game like slither.io [source] 🌐
ENGINES - DEG Mods - Decentralized Game Mods [info] [source] 🌐 - NG Engine - Nostr Game Engine [source] 🌐 - JmonkeyEngine - Java game engine [source] 🌐
Customization
Like other Services
- Olas - Instagram like [source] 🌐🍎🤖(on zapstore)
- Nostree - Linktree like 🌐
- Rabbit - TweetDeck like [info] 🌐
- Zaplinks - Nostr links 🌐
- Omeglestr - Omegle-like Random Chats [source] 🌐
General Uses
- Njump - HTML text gateway source 🌐
- Filestr - HTML midia gateway [source] 🌐
- W3 - Nostr URL shortener [source] 🌐
- Playground - Test Nostr filters [source] 🌐
Places
- Wherostr - Travel and show where you are
- Arc Map (Mapstr) - Bitcoin Map [info]
Driver and Delivery
- RoadRunner - Uber like [on development] ⏱️
- Nostrlivery - iFood like [on development] ⏱️
⚠️ SCAM ⚠️ | Arcade City - Uber like [source]
OTHER STUFF
Lightning Wallets (zap)
- Wallet of Satoshi - Simplest Lightning Wallet [info] 🤖🍎
- Coinos - Web wallet and Nostr client [source] 🌐
- Alby - Native and extension [info] [source] 🌐
- Minibits - Cashu mobile wallet [info] 🤖
- LNbits - App and extension [source] 🤖🍎💻
- Zeus - [info] [source] 🤖🍎
- Blink - Open source custodial wallet (KYC over 1000 usd) [source] 🤖🍎
⚠️ ZBD - Zap Gaming wallet and no more Social [closed source] [info] [some resources] 🤖 ⚠️ ZBD suddenly canceled my account for alleged Terms of Service violations, gives me no explanation and won't let me withdraw my money ⚠️
Without Zap - Wassabi Wallet - Privacy-focused and non-custodial with Nostr Update Manager [source]
Exchange
Media Server (Upload Links)
audio, image and video
Connected with Nostr (NIP):
- Nostr Build - Free and paid Upload [info] [source] 🌐
- NostrMedia - Written in Go with Nip 96 / Blossom (free and paid) [info] [source]
- Nostr Check - [info] [source] 🌐
- NostPic - [info] [source] 🌐
- Sovbit - Free and paid upload [info] [source] 🌐
- Voidcat - Nip-96 and Blossom [source] 🌐
- Primal Media - Primal Media Uploader [source] 🌐
Blossom - Your Media Safer
- Primal Blossom 🌐
- NostrBuild Blossom - Free upload (max 100MiB) and paid [info] [source] 🌐
Paid Upload Only
- Satellite CDN - prepaid upload (max 5GB each) [info] [source] 🌐
Without Nostr NIP:
- Pomf - Upload larger videos (max 1GB) [source]
- Catbox - max 200 MB [source]
- x0 - max 512 MiB [source]
Donation and payments
- Zapper - Easy Zaps [source] 🌐
- Autozap [source] 🌐
- Zapmeacoffee 🌐
- Nostr Zap 💻(numpy)
- Creatr - Creators subscription 🌐
- Geyzer - Crowdfunding [info] [source] 🌐
- Heya! - Crowdfunding [source]
Security
- Secret Border - Generate offline keys 💻(java)
- Umbrel - Your private relay [source] 🌐
Key signing/login and Extension
- Amber - Key signing [source] 🤖(on zapstore)
- Nowser - Account access keys 📱(🤖🍎) 💻(🐧🍎🪟)
- Nos2x - Account access keys 🌐
- Nsec.app 🌐 [info]
- Lume - [info] [source] 🐧🪟🍎
- Satcom - Share files to discuss - [info] 🌐
- KeysBand - Multi-key signing [source] 🌐
Code
- Stacks - AI Templates [info] [source] 🌐
- Nostrify - Share Nostr Frameworks 🌐
- Git Workshop (github like) [experimental] 🌐
- Gitstr (github like) [on development] ⏱️
- Osty [on development] [info] 🌐
- Python Nostr - Python Library for Nostr
- Sybil - Creating, managing and test Nostr events [on development] ⏱️
Relay Check and Cloud
- Nostr Watch - See your relay speed 🌐
- NosDrive - Nostr Relay that saves to Google Drive
Bidges and Getways
- Matrixtr Bridge - Between Matrix & Nostr
- Mostr - Between Nostr & Fediverse
- Nostrss - RSS to Nostr
- Rsslay - Optimized RSS to Nostr [source]
- Atomstr - RSS/Atom to Nostr [source]
Useful Profiles and Trends
nostr-voice - Voice note (just some clients)
NOT RELATED TO NOSTR
Voca - Text-to-Speech App for GrapheneOS [source] 🤖(on zapstore)
Android Keyboards
Personal notes and texts
Front-ends
- Nitter - Twitter / X without your data [source]
- NewPipe - Youtube, Peertube and others, without account & your data [source] 🤖
- Piped - Youtube web without you data [source] 🌐
Other Services
- Brave - Browser [source]
- DuckDuckGo - Search [source]
- LLMA - Meta - Meta open source AI [source]
- DuckDuckGo AI Chat - Famous AIs without Login [source]
- Proton Mail - Mail [source]
Other open source index: Degoogled Apps
Some other Nostr index on:
-
 @ 7460b7fd:4fc4e74b
2025-06-05 15:54:42
@ 7460b7fd:4fc4e74b
2025-06-05 15:54:42比特币正在主动引诱量子计算“破解自己”
引言:危机还是契机?
比特币和量子计算,这两个看似对立的存在,正在酝酿一场耐人寻味的博弈。许多人担心未来强大的量子计算机将秒破比特币的密码学基石,从而令区块链安全灰飞烟灭。然而,本文想传达的核心观点却截然相反:比特币不仅不会被量子破解打败,反而正在通过协议层的巧妙设计来“引诱”量子计算进入自己的游戏规则之中。通过诸如BIP-360等提案,比特币有望将量子计算的威胁转化为动力,开启一个“后挖矿时代”的全新正反馈经济体系,让“破解”本身成为新的挖矿机制。
这样的观点听起来近乎狂想,但背后有着深厚的技术逻辑支撑。我们将从基本的密码学原理谈起,逐步剖析量子计算的能力与局限,以及比特币协议在抗量子方向做出的结构性准备。最后,我们探讨一种大胆的经济模型:当量子计算被诱导去参与“破解竞赛”时,或许正是比特币凤凰涅槃、新经济形态崛起之机。
非对称加密的数学本质:“上帝视角”的陷门答案
非对称加密(如RSA、椭圆曲线加密ECC等)的核心在于存在一种单向函数:正向计算容易,反向推导极难。公钥可以视作某个难题的题目,私钥则相当于“上帝视角”提前知道的答案。一旦掌握私钥,就能轻松完成从答案到题目的逆推;而只有公钥时,想要逆推出私钥则被设计为在现实中不可行。这类单向难题通常通过陷门函数来实现——对合法持有者(私钥)来说,存在隐藏的捷径(陷门)可以快速解题;而对局外人来说,题目看似无解。
举例来说,比特币当前采用的ECC加密:私钥与公钥的关系就像“一次难以逆推的乘法”。给定私钥x,乘以基点G可轻易得到公钥点P = x·G,但已知P却无法高效求出x。这种不对称确保了签名者可以用私钥生成签名,而验证者只能用公钥验证签名而无法伪造。私钥掌握了解题的“上帝答案”,公钥则只能用于验证答案是否正确。
这一点在新型的抗量子算法中同样体现。以格密码(lattice cryptography)为例:Falcon等基于NTRU格的签名算法,其公钥可以被视为一个高维长基,私钥是对应的短基。pqshield.com在二维格子上的示意说明了这种不对称性:拥有短基(私钥)时,我们可以高效地找到距离某个目标点很近的格点解;但只有长基(公钥)时,我们顶多能验证某个给定解是否有效,却很难自行找到足够优质的解pqshield.com。换言之,私钥提供了一个陷门,允许持有者快速逆推答案,而公钥持有者只能望“题”兴叹。
图:在二维格子中,签名者持有的短基(私钥)可以高效求解出距离目标点(黑色方块)极近的格点解(绿色圆点)。绿色平行四边形表示短基下求解空间很小,因而容易找到最优解。这直观展示了陷门函数的威力:私钥掌握短基就如同拿到了解题捷径。
图:仅持有长基(公钥)时,使用相同算法得到的格点解(红色圆点)可能距离目标(黑色方块)很远。红色平行四边形代表在无陷门情况下求解范围巨大,找到最佳解极其困难。但验证者仍可用长基检查出某个解(如绿色点)确实是有效解pqshield.com。这体现了公私钥在计算能力上的不对称:私钥可求解,公钥仅可验证。
总而言之,非对称加密的安全性源自数学难题的单向性质和陷门结构。私钥就是那个隐藏的逆向通道,“上帝视角”的答案;公钥则是不具备捷径的信息,只够验证而无法逆推。从RSA的整数分解、ECC的离散对数,到Falcon的近似最近矢量问题,每一种公钥体制都是在构造“题目易出答案难逆”的格局,让持有陷门者轻松,旁观破解者绝望。
量子计算的原理与极限:并行穷举的神话与现实
量子计算机令人畏惧之处,在于其并行计算能力。通过量子叠加态,n个量子比特(qubit)可同时表示2^n种状态——仿佛能把指数级的可能性同时考虑。配合量子干涉与算法设计,量子计算机能够以远胜传统计算机的效率解决某些特定问题。其中最著名的就是Shor算法,它能在多项式时间内完成对大整数的质因数分解和离散对数求解。这正是传统公钥加密(RSA、ECC)的命门:一旦有足够强大的量子计算机,基于这些数学问题的公钥体制将不再困难,私钥可以由公钥“解密”而出coindesk.com。
然而,“并行穷举”的神话背后有严格的物理和工程学限制。首先是量子比特数量和质量的限制:当前的量子芯片规模远未达到破解现代加密所需的级别。据风险研究机构与专家调查,目前我们只有几十到几百个物理qubit,而要威胁256位ECC或2048位RSA,需要数百万高质量qubitdeloitte.com。不仅数量上相差几个数量级,现有量子芯片的纠错和降噪技术也远不成熟。量子比特极其敏感,微小噪声都会引入错误,真正实用的量子计算机需要对成千上万的物理比特进行纠错编码,形成稳定的逻辑比特。这个工程挑战之巨大,使得可攻破密码的量子计算机仍是多年之后的前景——多数专家预测大概还需十几年时间才可能出现实质威胁deloitte.com。
其次,量子计算并非万能破解,仅对特定问题有指数级加速。Shor算法擅长因数分解和离散对数,Grover算法可以对无结构的穷举搜索加速(将时间复杂度平方根降低)。但许多新兴的抗量子算法依赖的问题(如格上的最短向量问题SVP、最近向量问题CVP,或多变量方程、哈希预像等)目前并无高效量子算法。这些问题大多属于NP难类,甚至找近似解也极为困难emerginginvestigators.org。尽管量子计算提供并行试探能力,但对这类高度复杂的问题也爱莫能助。正如一项研究指出:SVP和CVP问题即便在量子计算机上依然“极端困难”,在可预见的将来仍足以保证安全性emerginginvestigators.org。Falcon所使用的NTRU格就是这样的难题代表——没有已知算法可以像Shor之于RSA那样,高效攻破NTRU问题。
最后,我们还需注意量子攻击的实际条件。量子破解比特币主要有两种情景:存储攻击和传输攻击deloitte.com。存储攻击指利用量子计算找出已公开公钥对应的私钥,从而盗取静态存放于链上某地址的币;传输攻击则是当交易广播(公钥暴露)后,在被矿工打包上链前的短暂窗口内,量子计算抢先推导私钥并盗转。这两种攻击对量子能力要求不同:存储攻击允许耗时几周甚至数月破解一个密钥,只要在币移动前完成即可;而传输攻击要求在区块确认之前(比特币约10分钟内,以太坊更短)秒破私钥deloitte.com。显然,目前和可预见的中期内,量子计算都远达不到传输攻击所需的即时破解水平;即便存储攻击,由于比特币区块链的UTXO模型(稍后详述),真正高价值、长时间暴露公钥的币也相对有限deloitte.com。因此,量子威胁虽然现实存在,但并非一夜之间让比特币崩溃的魔法。这反倒给予我们部署抗量子方案、引导量子力量“为我所用”的时间窗口。
抗量子密码学的三大结构前提
要让比特币真正抵御量子威胁,并把量子计算纳入自身生态,需要满足几个结构性前提。经过多年社区讨论和研究,以下三点被认为是比特币走向抗量子的关键设计要素:
-
UTXO模型:隐藏公钥缩短攻击窗口 – 比特币采用UTXO模型,每次交易都会生成新地址,公钥通常以哈希形式隐藏在地址中,直到你花费时才公布。这意味着量子计算只有在你发起交易后的很短时间内(交易确认前)才能获得公钥并尝试破解,大大压缩了攻击窗口anduro.iodeloitte.com。相较之下,账户模型(如以太坊)重复使用固定地址,公钥一旦被提取或首次使用后就长久暴露,使得65%以上的以太币当前都处于量子暴露风险中,而比特币约只有25%处于类似风险deloitte.com。UTXO模型通过“一次性地址”和“不用则公钥不出”的原则,天然提供了对抗量子存储攻击的第一道屏障。
-
“见证隔离”(SegWit):模块化升级签名算法 – 抗量子方案的发展日新月异,比特币必须保持签名算法的可插拔升级能力。2017年的见证隔离升级正是为此奠定基础:SegWit将签名等见证数据与交易本体分离,并引入版本化的见证脚本格式。这使得添加新签名类型成为可能——通过软分叉引入新的输出类型和见证版本,就能兼容地支持不同算法delvingbitcoin.org。正如BIP-341利用SegWit扩展出了Taproot的Schnorr签名,比特币也可以扩展出抗量子签名的新地址类型而无需硬分叉或显著增加区块体积delvingbitcoin.org。这一模块化特性对于迎接未来各类抗量子算法至关重要,没有SegWit的铺垫,抗量子改造将困难重重。
-
分级安全机制:根据价值和时效选择算法强度 – 由于UTXO的性质,每笔交易在花费时都会暴露其公钥。因此,安全策略不能“一刀切”,应允许根据币值大小或持有时长采用不同强度的抗量子算法。高价值的UTXO、长期未移动的“老币”,应使用更高安全级别但可能更重型的签名方案;反之,小额频繁交易可用较轻量的方案以兼顾效率和区块容量。好比Falcon提供了512和1024两种参数版本:Falcon-1024安全级别更高但签名稍大,而Falcon-512签名更小速度更快,适合资源受限场景emerginginvestigators.org。未来比特币或可同时支持多种抗量子算法或参数,用户按需选用,让“安全性”成为一种可以权衡和市场定价的链上资源。每一次支付都在安全与成本之间找到平衡,这将促使一个分层的安全市场形成——进一步论述见后文经济模型部分。
上述三大前提缺一不可:UTXO模型提供了基础的_安全缓冲_,SegWit机制给予_升级弹性_,分级算法让_经济可行性_落地。在这方面,比特币的体系结构远优于某些后来的公链。例如,以太坊的账户模型天生缺乏隐藏公钥的机制,地址就是固定的公钥哈希,一旦使用过私钥签名就永久暴露公钥,同时其交易脚本(EVM)对签名算法固定死,没有灵活插拔空间。这意味着以太坊想转向抗量子算法,必须经过极其痛苦的整体迁移或硬分叉——开发者需要为每个账户引入新密钥,新老算法并行过渡,智能合约地址、签名验证逻辑全部推倒重来。这种难度令人生畏,以至于有人嘲讽以太坊“几乎不可能”实现真正的抗量子迁移。反观比特币,得益于其简单而弹性的UTXO+Script设计,只需通过新的输出类型软分叉,就可以逐步引入抗量子地址,让用户自愿迁移过渡,避免一次性硬分叉的系统性风险。
BIP-360:可选抗量子签名,引入量子博弈
面对量子威胁,比特币开发社区并未坐以待毙。2024年,由开发者Hunter Beast提出的BIP-360提案(又称P2QRH,意为“支付到抗量子哈希”)正式将抗量子签名引入了议事日程anduro.io。BIP-360核心思路是在比特币中增加新的地址类型,这些地址采用后量子密码学的签名算法(当前优先考虑Falcon,并备选CRYSTALS-Dilithium和SPHINCS+等)来取代易受量子攻击的ECDSA/Schnorr签名anduro.iogroups.google.com。换句话说,用户可以自愿选择生成一种“抗量子地址”,对应的UTXO需使用抗量子算法签名才能解锁。
为什么说BIP-360让比特币“引诱”量子计算加入博弈?这里有几层含义:
首先,BIP-360采用软分叉方式部署,可选而非强制。这意味着在量子计算真正成熟之前,绝大多数交易仍可继续使用原有签名算法,不平添负担;而有安全偏好的用户或机构可以提前迁移一部分资金到抗量子地址以高枕无忧。随着量子技术进展,逐步会有更多人选择这个选项,形成一个与量子威胁赛跑的过程。这种自愿迁移机制本身就是一种对量子黑客的诱导:网络主动暴露出一个“堡垒更坚固”的区域,鼓励守法用户往那里走,同时意味着留下的旧区域反而成为显眼的攻击目标和“诱饵”。
其次,BIP-360在算法选择和参数上充分考虑了区块链经济的承受力。起初提案曾讨论过一些前沿算法如SQIsign,但发现其验证开销高达ECDSA的15,000倍,若全网采用将使验证一块新区块从1秒暴涨到4小时,带来难以接受的性能瓶颈groups.google.com。最终的方案优选Falcon等NIST标准算法,它们签名体积较小、验证高效,可与当前区块大小和验证速度相容groups.google.com。例如Falcon-1024的签名约1.3KB、公钥1.7KB左右,这虽然比当前64字节的Schnorr签名大得多,但并非无法承受。通过配置灵活的安全级别(如重要交易才用Falcon-1024,一般小额用Falcon-512或普通Schnorr),比特币区块空间将被合理分配在安全性和费用之间。BIP-360精心设计了新的地址格式和见证结构,确保即便引入抗量子签名,区块验证和存储开销也在经济范围内,不会动摇挖矿和节点运行的成本平衡anduro.io。
最后也是最具前瞻性的一点,BIP-360为量子计算参与链上博弈打开了一扇门。通过提供抗量子和非抗量子地址并存的环境,比特币网络其实设置了一个对量子计算的挑战擂台:量子计算可以选择去攻击那些仍使用旧签名算法且价值巨大的UTXO,但同一时间,网络里的用户也在不断提升关键UTXO的签名强度来应对。量子计算不再是一个纯粹的外部敌人,而被巧妙地“请”进了系统,在规则内与用户和矿工互动。这为下一节将讨论的新经济模型奠定了基础——破解即挖矿的雏形由此孕育。
值得一提的是,BIP-360还提出了一个Taproot的量子安全补丁方案P2TRH,用哈希隐藏Taproot的公钥以弥补其“公钥长曝”缺陷groups.google.comgroups.google.com。因为现有的Taproot地址(见证v1)是直接以公钥生成地址,失去了UTXO模型隐藏公钥的优势,量子攻击者可以随时尝试破解Taproot资金。P2TRH通过将Taproot公钥再哈希一层,恢复“见证前隐藏公钥”的特性,代价是每笔此类输入增加8.25字节开销groups.google.com。这显示出比特币开发者未雨绸缪,连新升级的Taproot漏洞也在想办法弥补,使全局达到抗量子的结构性统一。
综上,BIP-360及相关提案不仅提供了技术方案,更释放出一种积极的信号:比特币正主动拥抱量子挑战,将其纳入规则之内。正如Anduro团队支持BIP-360时所言:“量子攻击的威胁严肃而迫近,我们不能坐等紧急关头才手忙脚乱。”anduro.ioanduro.io比特币社区选择了在危机到来前主动布局,以最小的代价换取最大的安全冗余和发展新契机。
“破解竞赛”经济模型:当量子成为新矿工
设想未来5-15年内,量子计算技术逐步成熟。在比特币网络中,可能会上演这样一幕令人惊叹的图景:量子计算矿工和抗量子验证者同时在线,围绕着尚未升级的老式UTXO展开一场你追我赶的“破解竞赛”。这将引发怎样的经济动力?我们大胆描绘一个后PoW时代的可能场景:
一方面,强大的量子计算机不再浪费算力去挖掘哈希谜题(传统PoW),而是直接瞄准那些“量子易攻”的UTXO,即尚使用老式ECDSA/Schnorr签名且公钥已暴露的地址。这些地址里的币对合法持有人来说如果迟迟未迁移到抗量子地址,实际上就变成了躺在链上的“悬赏”:谁能先算出私钥,谁就能转走这些币。在量子计算参与者眼中,这些币和早期比特币矿工眼中的区块奖励无异,都是凭借算力可竞争获取的收益。值得注意的是,根据分析,目前约有25%的比特币(按币量)处于公钥已暴露状态deloitte.com。随着时间推移,这个比例可能上升——除非持有人主动升级安全。这就像网络故意留出了一片“牧场”,让量子计算在其中竞相捕猎,以获得收益。量子攻击者之间形成竞争:更快的量子芯片、更好的算法意味着可以更早破解特定私钥,拿下那笔币。这几乎就是PoW的变体——过去矿工拼SHA-256算力抢区块奖励,未来量子矿工拼质因数分解/离散对数能力抢遗留UTXO。
另一方面,守护这片“牧场”的则是抗量子验证者和普通用户自身的防范行为。所谓抗量子验证者,可能是运行完整后量子节点或提供安全服务的专业机构。他们一方面帮助用户升级UTXO(例如提供一键迁移服务,把旧地址币转移到新PQ地址上,收取服务费),另一方面监测全网可疑交易。当量子攻击者尝试盗取某UTXO时,如果该UTXO持有者事先购买了“安全服务”,验证者可以抢先代为花费将币转移到更安全的地址(类似白帽黑客行为),或者提供更高级别签名升级以挫败攻击。总之,抗量子能力本身也成为一种商品,在市场上明码标价。你想让自己的币绝对安全?可以付费请量子安全服务团队定期轮换密钥、使用最高强度签名、监控链上异常。你的交易想确保不中途被截胡?可以支付更高矿工费甚至指定量子保险节点护送。在链上,一个根据签名难度和安全级别定价的市场逐渐形成:越高难度的签名(比如超长位的Falcon变种、多重签名方案结合等)需要支付越高的费用来存储和验证;反过来,这些费用补贴给保障网络安全的矿工/节点,激励他们投入更多资源提升抗量子能力。这种正反馈循环下,“安全”本身成为了新的经济激励。
如此一来,比特币生态迎来了“后挖矿时代”的转型:当区块补贴逐渐趋零,原本空缺的矿工激励由量子破解竞赛和安全服务市场所填补。量子计算加入竞争并非摧毁网络,反而扮演起类似矿工的角色,通过攻破薄弱环节来获得收益;而诚实的参与者则通过不断升级安全措施和支付安全费用来保护资产。这看似矛盾,却形成了动态平衡:正如生物进化中的“红后效应”,猎豹越快,羚羊也进化得更快,两者共同提升了系统的活力。
当然,这一模型中也充满戏剧性和讽刺意味——尤其当我们把眼光投向其他缺乏这种机制的公链。以太坊等账户制链若在量子时代陷入危机,很可能只能选择停机硬分叉、或者由中心化机构出面更换用户密钥,几乎无自动博弈的空间可言。而比特币网络则通过精妙的协议调整,把外部威胁内化为内部博弈,让市场机制去调节和应对。这种弹性与活力,正是比特币经久不衰的原因。
结语:危机催生新生,量子力量为我所用
当年互联网面对计算机病毒肆虐时,人们最终没有被动防守,而是发展出杀毒产业、安全协议,将病毒的威胁转化为推动网络更加健壮的动力。同样道理,比特币面对量子计算的冲击,并非只能筑高墙固步自封,而是选择了更具前瞻性的道路:拥抱威胁、化敌为友。通过提前布局抗量子基础设施(UTXO模型、SegWit扩展、PQ签名算法)、逐步推行BIP-360等方案,比特币正悄然改变游戏规则。在这个新规则中,量量对决、攻守博弈将上演全新篇章,网络安全不再是一成不变的盾牌,而是一套动态进化的生态系统。
或许若干年后回望,我们会发现量子计算并没有摧毁比特币,反而成就了比特币历史上的一次重大飞跃——开启了一个后工作量证明时代的新纪元。在这个纪元里,“破解就是新挖矿”不再只是戏谑之语,而成为链上真实上演的经济现象;“出售安全”也从附属服务变成每个节点和用户的日常考量。比特币将继续履行其角色:作为一个去中心化的、自我强化的金融体系,它有能力将任何挑战转化为自身进化的燃料。
正如BIP-360提案作者所言,这是一个“when 而非 if”的议题anduro.io。量子计算终将到来,而比特币已在主动邀请它参与一场精心设计的游戏。当量子计算机真的站上擂台,比特币早已不再是那个任人宰割的靶子,而更像是一位早已摆好阵势的棋手,静候对手入局。在这盘大棋中,没有永远的猎物,只有不断进化的猎人。比特币,会是那个始终笑到最后的“猎人”吗?让我们拭目以待。
参考文献:
-
【18】PQShield博客:《Falcon – A Post-Quantum Signature Scheme》 – 阐释格密码中长基(公钥)与短基(私钥)的不对称性pqshield.com。
-
【28】Deloitte报告:《Quantum risk to the Ethereum blockchain》 – 比较了比特币UTXO模型与以太坊账户模型在量子攻击下的差异,指出以太坊65%资产易受量子威胁,而比特币约25%deloitte.comdeloitte.com。
-
【23】Bitcoin开发者论坛:《Proposing a P2QRH BIP towards a quantum resistant soft fork》 – 描述了通过SegWit扩展新签名算法的思路,无需硬分叉且不增加区块大小delvingbitcoin.org。
-
【22】Emerging Investigators论文:《A meta-analysis on NIST post-quantum cryptographic primitive finalists》 – 说明Falcon-512与Falcon-1024在安全性和性能上的差异,并强调SVP/CVP等问题对量子计算依然极为困难emerginginvestigators.orgemerginginvestigators.org。
-
【36】Anduro博客:《Bitcoin Needs Quantum Resistant Addresses – We Support BIP360》 – 介绍了BIP-360提案内容,引入抗量子地址类型P2QRH,采用Falcon和Dilithium签名,软分叉兼容anduro.io。同时强调量子威胁需提早应对的紧迫性anduro.ioanduro.io。
-
【32】Bitcoin开发邮件列表:《P2QRH/BIP-360 Update》 – 提供了BIP-360提案的最新动态,算法选型从SQIsign转向Falcon、Dilithium、SPHINCS+,原因是前者验证开销过大(15,000倍)而不切实际groups.google.comgroups.google.com。
-
【30】CoinDesk报道:《Quantum Computing Could Break Bitcoin-Like Encryption Far Easier…》 – 提及比特币所用ECC也可被Shor算法破解,只要有足够强大的量子计算机coindesk.com。
-
【33】Deloitte报告:《Quantum risk to the Ethereum blockchain》 – 阐述当前量子计算的物理局限:需要上百万qubit且降低噪声量级,目前技术远不能攻击密码算法deloitte.com。
-
【38】Bitcoin开发邮件列表:《P2QRH/BIP-360 Update》 – 描述了针对Taproot的P2TRH抗量子方案,用哈希隐藏公钥以减小长时间暴露,并分析其开销和局限groups.google.comgroups.google.com。
-
-
 @ da8b7de1:c0164aee
2025-06-04 16:37:07
@ da8b7de1:c0164aee
2025-06-04 16:37:07Nukleáris politika és szabályozási fejlemények
A Nemzetközi Atomenergia-ügynökség (IAEA) Kormányzótanácsa 2025. június 9-én kezdi meg szokásos júniusi ülését Bécsben. A főbb napirendi pontok között szerepel a 2024-es éves jelentés, a technikai együttműködési tevékenységek, az iráni ellenőrzés és felügyelet, az ellenőrzések végrehajtása Észak-Koreában és Szíriában, a nukleáris biztonság és védelem Ukrajnában, valamint a nukleáris anyagok átruházása és ellenőrzése az AUKUS-keretében. Az ülésen új tagokat is kijelölnek a Kormányzótanácsba, és előkészítik a 69. rendes közgyűlést[iaea.org].
Jelentős projektek és iparági bővülés
Az amerikai Tennessee Valley Authority (TVA) benyújtotta kérelmét az Egyesült Államok Nukleáris Szabályozási Bizottságához egy GE Vernova Hitachi BWRX-300 kis moduláris reaktor (SMR) megépítésére a Clinch River telephelyen, ami jelentős lépés az amerikai fejlett nukleáris technológiák elterjesztésében[world-nuclear-news.org]. Kanadában a hatóság engedélyezte az Ontario Power Generation számára, hogy egy BWRX-300 reaktort építsen a Darlington New Nuclear Project helyszínen, ezzel tovább haladva az észak-amerikai SMR-projektek terén[world-nuclear-news.org].
India nukleáris szabályozója jóváhagyta a négyblokkos Mahi Banswara Rajasthan Atomerőmű telephelyét, Kínában pedig folytatódnak a szerelési munkák a Haiyang 3 egységen. Eközben Belgium és Dánia felülvizsgálják nukleáris politikájukat: Belgium visszavonja a korábbi leállítási döntést, Dánia pedig újragondolja álláspontját[world-nuclear-news.org].
Ellátási lánc, munkaerő és nemzetközi együttműködés
A nukleáris kapacitás várható gyors növekedése miatt egyre nagyobb hangsúly kerül mind a helyi, mind a globális ellátási lánc felkészítésére. A World Nuclear Association legutóbbi konferenciája kiemelte az ellátási lánc „globalizációjának” fontosságát a bővülés támogatásához[world-nuclear-news.org]. A nukleáris munkaerő világszerte növekedni fog, ami új lehetőségeket teremt, nem pedig hiányt. Az iparági szakértők hangsúlyozzák a jelentkezők tapasztalatának javítását és a szektorok közötti készségek hasznosítását a jövőbeni igények kielégítésére[world-nuclear-news.org].
A nemzetközi szabályozói együttműködés is fejlődik, különösen a kis moduláris reaktorok (SMR) tervezési értékelése terén. A brit Nukleáris Szabályozási Hivatal közzétette első jelentését ebben a témában, globális szinten hatékonyabb és összehangoltabb megközelítést célozva[world-nuclear-news.org].
Gazdasági és befektetési trendek
A nukleáris szektorban újra optimizmus tapasztalható, egészséges projektportfóliókkal és növekvő magánbefektetésekkel, különösen a fejlett üzemanyagok, például a HALEU (magas dúsítású urán) terén. A Világbank lehetséges politikai váltása, amely lehetővé tenné nukleáris projektek finanszírozását, jelentős hatással lehet a globális befektetésekre, példát mutatva más hitelezőknek is[ans.org].
Az USA-ban jelentős lépés a Prohibiting Russian Uranium Imports Act életbe lépése, amely megtiltja a feldolgozatlan, alacsony dúsítású orosz urán behozatalát, és 2,72 milliárd dollár szövetségi támogatást szabadít fel a hazai urántermelés fellendítésére. A törvény 2027-ig korlátozott mentességeket engedélyez, 2040-ben pedig lejár[ans.org].
Technológia és innováció
A TerraPower hivatalosan is jelezte a brit hatóságoknak, hogy megkezdi a Natrium nátrium-hűtésű gyorsreaktor általános tervezési engedélyezési folyamatát, ezzel jelezve, hogy a vállalat nemzetközi szinten is be kívánja vezetni ezt a technológiát[world-nuclear-news.org]. Olaszországban új nemzeti bizottság alakult a radioaktív anyagok szállításával kapcsolatos kihívások kezelésére, a megfelelőség és a logisztika egyszerűsítése érdekében[world-nuclear-news.org].
Az Enel, az Ansaldo Energia és a Leonardo megalapította a Nuclitalia céget, hogy tanulmányozza a fejlett nukleáris technológiákat és elemezze a piaci lehetőségeket, ami jól mutatja az európai érdeklődés növekedését a következő generációs nukleáris megoldások iránt[world-nuclear-news.org].
Friss és közelgő események
- Az IAEA Kormányzótanácsának ülése (2025. június 9–13.) számos politikai, biztonsági és védelmi kérdéssel foglalkozik majd[iaea.org].
- Az amerikai Fehér Ház nemrégiben csúcstalálkozót tartott a hazai nukleáris fejlesztésekről, és elindította a legnagyobb szövetségi kezdeményezést az elmúlt ötven évben a hálózati méretű nukleáris reaktorok felgyorsított építésére[ans.org].
Források: - world-nuclear-news.org - iaea.org - ans.org - nucnet.org
-
 @ 975e4ad5:8d4847ce
2025-06-05 13:14:46
@ 975e4ad5:8d4847ce
2025-06-05 13:14:46What is the Fiat System and How Do Central Banks Set Interest Rates?
When central banks expand credit, they often increase the money supply by creating new money through mechanisms like quantitative easing (QE). For instance, a central bank may purchase government bonds, injecting money into the economy. This boosts liquidity but can lead to inflation when too much money chases limited goods and services.
Low interest rates make borrowing cheaper, encouraging spending and investment. However, this can overheat the economy, create speculative bubbles (e.g., in real estate), and drive inflation. Conversely, high interest rates restrict borrowing, slow the economy, and curb inflation but may trigger recessions.
How Would Interest Rates Work Under a Bitcoin Standard?
Under a Bitcoin standard, the money supply is fixed—only 21 million bitcoins will ever exist, with the last one mined around 2140. Unlike the fiat system, no central authority can manipulate the money supply or set interest rates. Instead, interest rates would be determined entirely by the market—by the supply and demand for capital.
If someone wants to borrow bitcoins, the interest rate would depend on negotiations between the lender and borrower. For example, if demand for loans is high and available bitcoins are scarce, interest rates would rise. Conversely, if there are ample bitcoin savings, rates might fall. This process would be fully decentralized and reflect real market conditions, not central bank decisions.
Since new bitcoins cannot be “printed,” there would be no inflation caused by an expanding money supply. Instead, bitcoin’s value would likely rise over time (deflation) as its fixed supply competes with growing demand. This could encourage saving over reckless spending, reshaping economic behavior.
Advantages of a Bitcoin Standard
-
Protection Against Inflation: Bitcoin’s fixed supply prevents currency devaluation, a common issue with fiat money. This safeguards savings and promotes long-term planning.
-
Decentralization: Without a central bank manipulating the market, economic decisions are made by individuals, not bureaucrats. This aligns with free-market principles where competition and innovation thrive.
-
Transparency and Security: The Bitcoin blockchain is public and immutable, ensuring transactions are transparent and secure from tampering.
-
Financial Freedom: Under a Bitcoin standard, individuals have full control over their money without government or bank interference, which is especially crucial in countries with unstable regimes or currencies.
-
Discipline in Lending: Without the ability to print money, lenders would be more cautious, reducing risky investments and speculative bubbles.
Potential Drawbacks and Why a Bitcoin Standard is Superior
One major argument against a Bitcoin standard is that it could slow economic growth. Low interest rates in the fiat system encourage borrowing and spending, driving economic activity. Under a Bitcoin standard, where interest rates are market-driven and likely higher, borrowing would be costlier, potentially limiting investments in new projects.
However, this critique misses a key point: economic growth fueled by artificially low interest rates and money printing is often unsustainable. It leads to debt crises, inflation, and bubbles that eventually burst, as seen in 2008. A Bitcoin standard promotes healthy economic discipline, where investments are based on real value, not artificial capital.
Moreover, bitcoin’s deflationary nature could shift how people view money. Instead of chasing endless growth, societies might prioritize sustainability, innovation, and efficiency. This could lead to a more stable and equitable economy in the long run.
Additional Considerations
A Bitcoin standard could transform global trade. Today, countries with fiat currencies often manipulate exchange rates to gain trade advantages. With bitcoin as a universal currency, such manipulations would vanish, fostering fairer competition.
Another aspect is energy efficiency. While bitcoin mining consumes energy, it incentivizes the development of renewable sources as miners seek cheap, sustainable energy. This could accelerate the transition to a green economy.
Conclusion
The Bitcoin standard offers a vision of an economy rooted in sound money, free markets, and financial freedom. While it may slow certain aspects of economic growth, it creates a more stable and sustainable system that protects individuals from inflation and centralized control. In a world where trust in institutions is waning, the Bitcoin standard is a step toward a fairer and more transparent future.
-
-
 @ cae03c48:2a7d6671
2025-06-05 15:01:26
@ cae03c48:2a7d6671
2025-06-05 15:01:26Bitcoin Magazine
How Strategy (MSTR) Built Their Capital Stack to Accelerate Bitcoin AccumulationMicroStrategy—now operating as Strategy
 —has built the most aggressive Bitcoin treasury in the world. But its true innovation isn’t just holding Bitcoin. It’s in how it finances the accumulation of Bitcoin at scale without giving up control or diluting shareholder value.
—has built the most aggressive Bitcoin treasury in the world. But its true innovation isn’t just holding Bitcoin. It’s in how it finances the accumulation of Bitcoin at scale without giving up control or diluting shareholder value.The engine behind this? A meticulously designed capital stack—a multi-tiered structure of debt, preferred stock, and equity that appeals to different types of investors, each with unique risk, yield, and volatility preferences.
This is more than corporate finance—it’s a blueprint for Bitcoin-native capital formation.
What Is a Capital Stack?
A capital stack refers to the layers of capital a company uses to finance its operations and strategic goals. Each layer has its own return profile, risk level, and repayment priority in the event of liquidation.
Strategy’s capital stack is designed to do one thing exceptionally well: convert fiat capital into Bitcoin exposure—efficiently, at scale, and without compromise.
The Stack: Ordered by Priority
Strategy’s capital stack comprises five core instruments:
1. Convertible Notes
2. Strife Preferred Stock ($STRF)
3. Strike Preferred Stock ($STRK)
4. Stride Preferred Stock ($STRD)
5. Common Equity ($MSTR)These layers are ranked from highest to lowest in repayment priority. What makes this structure unique is how each layer balances downside protection, yield, and Bitcoin exposure—offering institutional investors fixed-income alternatives with varying degrees of correlation to Bitcoin.
Strategy’s Capital Stack illustrated by Chris Millas
Convertible Notes: Senior Debt with Optional Upside
Strategy’s capital stack begins with convertible notes—senior unsecured debt that can convert into equity.
- Downside: Low risk, high priority in liquidation
- Upside: Modest unless converted
- Appeal: Institutional debt investors seeking protection with optional Bitcoin-adjacent upside
These notes were Strategy’s earliest fundraising tools, enabling the company to raise billions in low-interest environments to accumulate Bitcoin without issuing equity.
Strife ($STRF): Investment-Grade Yield
Strife is a perpetual preferred stock designed to mimic high-grade fixed income.
- 10% cumulative dividend, paid in cash
- $100 liquidation preference
- No conversion rights or Bitcoin upside
- Compounding penalties on unpaid dividends
- Low volatility, medium risk profile
Strife targets conservative capital—allocators who want predictable income without equity or crypto exposure. It’s senior to other preferreds and common stock, making it a high-quality fixed-income proxy built atop a Bitcoin treasury.
Strike ($STRK): Yield + Bitcoin Optionality
Strike is convertible preferred stock—bridging fixed income and equity upside.
- 8% cumulative dividend
- Convertible into $MSTR at $1,000 strike
- Paid in cash or Class A shares
- Bitcoin exposure via conversion option
- Medium volatility, low risk
Strike appeals to investors who want income with optional participation in Bitcoin upside. In bullish Bitcoin cycles, the conversion option becomes valuable—offering a hybrid between bond-like stability and equity-like potential.
Stride ($STRD): High Yield, High Risk
Stride is the most junior preferred—non-cumulative, perpetual stock issued with high yield and few protections.
- >10% dividend, only if declared
- No compounding, no conversion, no voting rights
- Highest relative risk among preferreds
- Liquidation priority above common equity, but below all others
Stride plays a crucial role. Its issuance improves the credit quality of Strife, adding a subordinate capital buffer beneath it—similar to how mezzanine debt protects senior tranches in structured finance.
Stride attracts yield-hungry investors, enabling Strategy to raise capital without compromising more senior layers.
Common Equity ($MSTR): Pure Bitcoin Beta
At the base is Strategy’s common equity—the most volatile, least protected, but highest potential instrument in the stack.
- Unlimited upside
- No dividend, no priority
- Full exposure to Bitcoin volatility
- Voting rights, long-term ownership
Common equity is for conviction-driven investors. Over the past four years, this layer has attracted capital from funds and individuals aligned with Strategy’s Bitcoin thesis—investors who want maximal upside from a corporate Bitcoin strategy.
The Big Picture: Saylor Is Targeting the Fixed Income Market
This isn’t just a financing mechanism—it’s a direct challenge to the $130 trillion global bond market.
By issuing instruments like $STRF, $STRK, and $STRD, Strategy is offering Bitcoin-adjacent yield vehicles that absorb demand from across the capital spectrum:
- Institutional investors seeking investment-grade yield
- Hedge funds chasing structured upside
- Yield hunters willing to go down the stack for returns
Each instrument behaves like a synthetic bond, yet all are backed by a Bitcoin accumulation engine.
As Director of Bitcoin Strategy at Metaplanet, Dylan LeClair put it: “Saylor is coming for the entire fixed income market.”
Rather than issue traditional bonds, Saylor is constructing a Bitcoin-native capital stack—one that unlocks liquidity without ever selling the underlying asset.
Why It Matters: A Model for Bitcoin Treasury Strategy
Strategy’s capital structure is more than innovation—it’s a financial operating system for any public company that wants to monetize Bitcoin’s rise while maintaining capital discipline.
Key takeaways:
- Every layer matches a specific investor need: From low-risk debt to speculative yield
- Capital flows in, Bitcoin stays put: Preserving treasury position while scaling
- No single instrument dominates: The stack is diversified by design
- Control is retained: Most securities are non-voting, non-convertible
For corporations serious about building a Bitcoin-native balance sheet, this is the playbook to study.
Saylor isn’t just stacking Bitcoin—he’s engineering the financial infrastructure for a monetary paradigm shift.
Disclaimer: This content was written on behalf of Bitcoin For Corporations. This article is intended solely for informational purposes and should not be interpreted as an invitation or solicitation to acquire, purchase, or subscribe for securities.
This post How Strategy (MSTR) Built Their Capital Stack to Accelerate Bitcoin Accumulation first appeared on Bitcoin Magazine and is written by Nick Ward.
-
 @ a5ee4475:2ca75401
2025-06-04 14:31:23
@ a5ee4475:2ca75401
2025-06-04 14:31:23[EM ATUALIZAÇÃO]
vacina #saude #politica #manipulacao #mundial #genocidio #pandemia #conspiracao
Este artigo reúne algumas evidências mais antigas que vim registrando durante alguns anos contra a covid, vacinas obrigatórias e a ação de agências de governo, fundações, políticos, mídia tradicional, celebridades, influenciadores, cientistas, redes sociais e laboratórios, em envolvimento com genocídio e restrições de liberdades em escala mundial causado por decisões em várias esferas relativas ao covid e as vacinas obrigatórias em geral.
Porém, alguns links podem não estar mais disponiveis, foram que ainda faltam ser registradas muitas informações já divulgadas nos últimos anos e que não tivemos contato pela escassez de meios para a obtenção dessas informações de forma organizada. Portanto, o presente artigo ainda passará por atualizações de conteúdo e formatação, então se possível ajudem sugerindo com complementos ou alterações.
Explicações iniciais:
- Sars-Cov-2 é que é nome do vírus. Ele que causa a doença Covid-19;
- O Sars-Cov-2 é o segundo tipo de Sars-Cov documentado, o primeiro ocorreu em 2003;
- 'Coronavírus' na verdade é um nome genérico para vários vírus de gripes já comuns, dado para o tipo corona (com uma "coroa", 'espetos' ao redor dele), o Sars-Cov-2 é só uma delas.
1. Vacinas Obrigatórias em Geral
-
Vacinas e autismo em crianças https://publichealthpolicyjournal.com/vaccination-and-neurodevelopmental-disorders-a-study-of-nine-year-old-children-enrolled-in-medicaid/
-
O CDC admite que 98 milhões de pessoas receberam o vírus do câncer através da vacina da Poliomielite https://medicinanews.com.br/frente/frente_1/o-cdc-admite-que-98-milhoes-de-pessoas-receberam-o-virus-do-cancer-atraves-da-vacina-poliomielite/
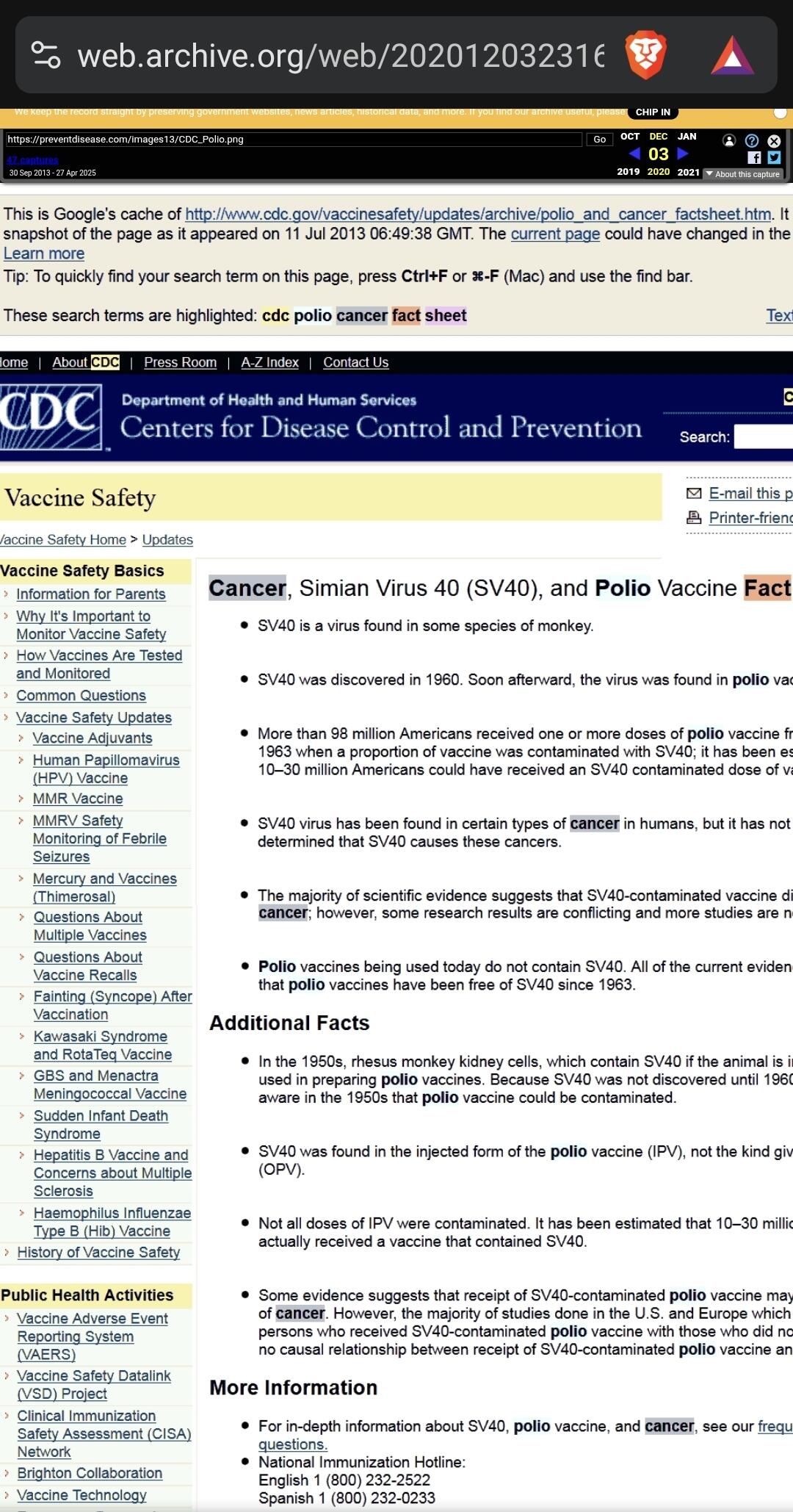 - Fonte original da imagem: https://preventdisease.com/images13/CDC_Polio.png [indisponível]
- Imagem arquivada em: https://web.archive.org/web/20201203231640/
- Fonte original da imagem: https://preventdisease.com/images13/CDC_Polio.png [indisponível]
- Imagem arquivada em: https://web.archive.org/web/20201203231640/"O CDC (Os Centros de Controle e Prevenção de Doenças dos Estados Unidos) removeu rapidamente uma página do seu site, que estava em cache no Google, como você pode ver logo abaixo, admitindo que mais de 98 milhões de americanos receberam uma ou mais doses de vacina contra pólio dentro de 8 período entre 1955 e 1963, quando uma proporção da vacina foi contaminada com um poliomavírus causador de câncer chamado SV40."
27/02/2021 - Por que o Japão demorou para vacinar, mesmo com Olimpíada se aproximando https://www.cnnbrasil.com.br/internacional/2021/02/27/por-que-o-japao-demorou-para-vacinar-mesmo-com-olimpiada-se-aproximando
"Desconfiança da população japonesa em relação a vacinas, ligada a casos ocorridos no passado, está entre razões que atrasaram imunização no país.
A resistência à vacina do Japão remonta à década de 1970, quando duas crianças morreram dentro de 24 horas após receberem a vacina combinada contra difteria, tétano e coqueluche (coqueluche). A vacina foi temporariamente suspensa, mas a confiança já havia sido abalada. Por vários anos, as taxas de vacinação infantil caíram, levando a um aumento nos casos de tosse convulsa.
No final dos anos 1980, houve outro susto com a introdução da vacina tripla contra sarampo, caxumba e rubéola produzida no Japão. As primeiras versões do imunizante foram associadas à meningite asséptica, ou inchaço das membranas ao redor do cérebro e da medula espinhal. O problema foi rastreado até o componente caxumba da vacina tripla, o que levou a uma ação judicial e a indenização por danos pesados.
O Instituto Nacional de Ciências da Saúde interrompeu a dose combinada em 1993 e a substituiu por vacinas individuais. Após o escândalo, Shibuya disse que o governo japonês se tornou "ciente dos riscos" e seu programa nacional de vacinação tornou-se voluntário.
O Dr. Yuho Horikoshi, especialista em doenças infecciosas, diz que os processos levaram a uma "lacuna de vacinação", em que nenhuma vacina foi aprovada no Japão por cerca de 15 anos.
Mais recentemente, em 2013, o Japão adicionou a vacina contra o papilomavírus humano (HPV) ao calendário nacional para proteger as meninas contra o vírus sexualmente transmissível, que é conhecido por causar câncer cervical. No entanto, vídeos de meninas supostamente sofrendo de reações adversas começaram a circular no YouTube, levando o governo a retirá-los da programação nacional."
2. PRIMEIRAS OCORRÊNCIAS PREDITIVAS AO COVID-19
2010 - Fundação Rockfeller, Lockstep. https://www.rockefellerfoundation.org/wp-content/uploads/Annual-Report-2010-1.pdf
Neste PDF da fundação Rockfeller, em seu próprio site, a fundação deixou claro o seu envolvimento em casos de ‘contenção’ de pandemias juntamente com a USAID (agência americana com nome ambíguo, como formalmente ‘United States Agency for International Development’, mas soando como ‘US Socorre’, mas sendo um braço do governo democrata que financiava interferências políticas diretas em vários países, como no Brasil: https://www.gazetadopovo.com.br/vida-e-cidadania/quais-ongs-cooperaram-com-moraes-e-sao-alvo-do-congresso-nos-eua/ ), inclusive em relacionadas ao SARS, um vírus muito semelhante ao SEGUNDO tipo de vírus Sars-Cov, o Sars-Cov-2 (o vírus propagado em 2019) e que causa o COVID-19.
Segundo eles:
“Integração entre Regiões e Países
A Fundação Rockefeler investiu US$ 22 milhões em sua Iniciativa de Redes de Vigilância de Doenças para ajudar a conter a disseminação de doenças infecciosas e pandemias, fortalecendo os sistemas nacionais, regionais e globais de vigilância e resposta a doenças. Dois programas-chave da Rockefeler — a Rede de Vigilância de Doenças da Bacia do Mekong e a Rede Integrada de Vigilância de Doenças da África Oriental — conectaram e capacitaram profissionais de saúde, epidemiologistas e autoridades de saúde pública em toda a região, levando a um aumento de seis vezes nos locais de vigilância de doenças transfronteiriças somente nos últimos três anos. Em 2010, a Rockefeler expandiu a bem-sucedida campanha transdisciplinar One Health, que a USAID e o Banco Asiático de Desenvolvimento adotaram como modelos. One Health refere-se à integração da ciência médica e veterinária para combater essas novas variedades de doenças zoonóticas que se movem e sofrem mutações rapidamente de animais para humanos. Essas colaborações criaram e fortaleceram uma rede regional crítica de saúde pública, enquanto as lições aprendidas foram exportadas entre disciplinas e países. Além de fortalecer os laços globais em saúde pública, a Rockefeler ajudou a elevar o nível de especialização e treinamento em campo. O Programa de Treinamento em Epidemiologia de Campo coloca graduados nos mais altos escalões do governo no Laos e no Vietnã, enquanto as bolsas da Rockefeler transformaram as ferramentas disponíveis para os médicos, permitindo-lhes utilizar o poder da internet para se comunicar e monitorar eventos, compreender contextos locais e analisar novos problemas. Finalmente, estamos aplicando ferramentas do século XXI para combater os desafios de saúde do século XXI.”
Julho de 2012 - Revista Mundo Estranho
Houve uma "coincidência", a revista Mundo Estranho em julho de 2012, entrevistou o até então doutorando em virologia, Átila Iamarino (o mesmo cientista que fez diversas propagandas das vacinas no Brasil), para descrever um possível cenário de propagação de uma epidemia viral, a revista descreve com grande precisão os eventos de 2020, mas apontando o oposto da China, em que, na realidade, sua economia cresceu vertiginosamente.
3. PRIMEIROS INDÍCIOS
10/2019 - Evento 201 - Durante os Jogos Militares Internacionais na China https://www.centerforhealthsecurity.org/event201/
Promovido por: - Bill & Melinda Gates Foundation - John Hopkins Institute - Fórum econômico mundial
"O evento simula a liberação de um coronavírus novo do tipo zoonótico transmitido por morcegos para porcos e por fim para humanos. Eventualmente ele se torna muito transmissível entre humanos levando a uma pandemia severa. O vírus é muito parecido com o vírus da SARS, mas se transmite muito mais facilmente entre pessoas devido a sintomas muito mais leves destas."
Também mencionado por: [Jornal Estadão] ( http://patrocinados.estadao.com.br/medialab/releaseonline/releasegeral-releasegeral/geral-johns-hopkins-center-for-health-security-forum-economico-mundial-e-fundacao-bill-melinda-gates-realizam-exercicio-pandemico-e-transmissao-ao-vivo/)
Sobre o "Movimento antivacina"
05/12/2017 - Movimento antivacina: como surgiu e quais consequências ele pode trazer? https://www.uol.com.br/universa/noticias/redacao/2017/12/05/o-que-o-movimento-antivacina-pode-causar.htm?cmpid=copiaecola
23/03/2019 - "Instagram bloqueia hashtags e conteúdo antivacinação" https://canaltech.com.br/redes-sociais/instagram-bloqueia-hashtags-e-conteudo-antivacinacao-135411/
23/05/2021 - Novos dados sobre pesquisadores de Wuhan aumentam debate sobre origens da Covid https://www.cnnbrasil.com.br/saude/novos-dados-sobre-pesquisadores-de-wuhan-aumentam-debate-sobre-origens-da-covid/
"A China relatou à Organização Mundial da Saúde que o primeiro paciente com sintomas semelhantes aos de Covid-19 foi registrado em Wuhan em 8 de dezembro de 2019"
01/02/2020 - O que aconteceu desde que o novo coronavírus foi descoberto na China https://exame.com/ciencia/o-que-aconteceu-desde-que-o-novo-coronavirus-foi-descoberto-na-china/
"O primeiro alerta foi recebido pela Organização Mundial da Saúde (OMS) em 31 de dezembro de 2019"
15/09/2020 - YouTube diz que vai remover vídeos com mentiras sobre vacina contra COVID-19 https://gizmodo.uol.com.br/youtube-remover-videos-mentiras-vacina-covid-19/
"O YouTube anunciou na quarta-feira (14) que estenderá as regras atuais sobre mentiras, propaganda e teorias da conspiração sobre a pandemia do coronavírus para incluir desinformação sobre as vacinas contra a doença.
De acordo com a Reuters, a gigante do vídeo diz que agora vai proibir conteúdos sobre vacinas contra o coronavírus que contradizem “o consenso de especialistas das autoridades de saúde locais ou da OMS”, como afirmações falsas de que a vacina é um pretexto para colocar chips de rastreamento nas pessoas ou que irá matar ou esterilizar quem tomar."
*07/01/2021 - YouTube vai punir canais que promovem mentiras sobre eleições – incluindo os de Trump https://olhardigital.com.br/2021/01/07/noticias/youtube-vai-punir-canais-que-promovem-mentiras-sobre-eleicoes-incluindo-os-de-trump/
"O YouTube anunciou que vai punir canais que promovem mentiras sobre as eleições, removendo sumariamente qualquer vídeo que contenha desinformação e, ao mesmo tempo, advertindo com um “strike” o canal que o veicular. A medida já está valendo e a primeira “vítima” é ninguém menos que o ex-presidente americano, Donald Trump.
A medida não é exatamente nova, mas foi novamente comunicada e reforçada pelo YouTube na quarta-feira (6), após os eventos de invasão do Capitólio, em Washington, onde o presidente eleito Joe Biden participava da cerimônia que confirmava a sua vitória nas eleições de novembro de 2020. A ocasião ficou marcada pela tentativa de invasão de correligionários de Trump, que entraram no edifício em oposição à nomeação do novo presidente. Uma mulher acabou sendo morta pela polícia que protegia o local.
O ex-presidente Donald Trump teve vídeos banidos de seu canal no YouTube após os eventos de ontem (6) no capitólio."
4. FIGURAS CENTRAIS
Bill Gates
- Bill Gates diz 'não' a abrir patentes de vacinas https://www.frontliner.com.br/bill-gates-diz-nao-a-abrir-patentes-de-vacinas/
"Bill Gates, um dos homens mais ricos do mundo, cuja fundação tem participação na farmacêutica alemã CureVac, produtora de vacina mRNA para prevenção de covid-19, disse não acreditar que a propriedade intelectual tenha algo a ver com o longo esforço global para controlar a pandemia."
João Doria e São Paulo
26/07/2017 - João Dória vai a China conhecer drones para ampliar segurança eletrônica na capital paulista https://jc.ne10.uol.com.br/blogs/jamildo/2017/07/26/joao-doria-vai-china-conhecer-drones-para-ampliar-seguranca-eletronica-na-capital-paulista/
02/08/2019 - Governo de SP fará Missão China para ampliar cooperação e atrair investimentos https://www.saopaulo.sp.gov.br/spnoticias/governo-de-sao-paulo-detalha-objetivos-da-missao-china/
20/11/2019 - Doria se encontra com chineses das gigantes CREC e CRCC e oferece concessões de rodovia, metrô e ferrovia https://diariodotransporte.com.br/2019/11/20/doria-se-encontra-com-chineses-das-gigantes-crec-e-crcc-e-oferece-concessoes-de-rodovia-metro-e-ferrovia/
25/01/2020 - "Chineses serão agressivos" nas privatizações em SP até 2022, afirma Dória https://noticias.uol.com.br/colunas/jamil-chade/2020/01/25/entrevista-joao-doria-privatizacoes-sao-paulo-china.htm
O governador de São Paulo, João Doria, afirma que vai acelerar os programas de desestatização no estado em 2020 e acredita que concessões e vendas poderão permitir uma arrecadação de pelo menos R$ 40 bilhões. Nesse processo, o governador avalia que a China deve atuar de forma agressiva e que aprofundará sua posição de maior parceira comercial do estado, se distanciando de americanos e argentinos.
29/06/2020 - Doria estabelece multa para quem estiver sem máscara na rua em SP https://veja.abril.com.br/saude/doria-estabelece-multa-para-quem-estiver-sem-mascara-na-rua/
24/12/2020 - Doria é flagrado sem máscara e fazendo compras em Miami https://pleno.news/brasil/politica-nacional/doria-e-flagrado-sem-mascara-e-fazendo-compras-em-miami.html
"Foto do governador de São Paulo sem o item de proteção viralizou nas redes"
07/06/2021 - Doria é criticado na internet por tomar sol sem máscara em hotel no Rio https://vejasp.abril.com.br/cidades/doria-e-criticado-na-internet-por-tomar-sol-sem-mascara-em-hotel-no-rio/
30/09/2020 - Governo de SP assina contrato com Sinovac e prevê vacina para dezembro https://agenciabrasil.ebc.com.br/saude/noticia/2020-09/governo-de-sp-assina-contrato-com-sinovac-e-preve-vacina-para-dezembro
O governador de São Paulo, João Doria, e o vice-presidente da laboratório chinês Sinovac, Weining Meng, assinaram hoje (30), um contrato que prevê o fornecimento de 46 milhões de doses da vacina CoronaVac para o governo paulista até dezembro deste ano.
O contrato também prevê a transferência tecnológica da vacina da Sinovac para o Instituto Butantan, o que significa que, o instituto brasileiro poderá começar a fabricar doses dessa vacina contra o novo coronavírus. O valor do contrato, segundo o governador João Doria é de US$ 90 milhões.
20/10/2020 - Coronavac terá mais de 90% de eficácia, afirmam integrantes do governo paulista https://www.cnnbrasil.com.br/saude/2020/12/20/coronavac-tera-mais-de-90-de-eficacia-afirmam-integrantes-do-governo
24/10/2020 - Não esperamos 90% de eficácia da Coronavac’, diz secretário de saúde de SP https://www.cnnbrasil.com.br/saude/2020/12/24/nao-esperamos-90-de-eficacia-da-coronavac-diz-secretario-de-saude-de-sp
07/01/2021 - Vacina do Butantan: eficácia é de 78% em casos leves e 100% em graves https://www.cnnbrasil.com.br/saude/2021/01/07/vacina-do-butantan-eficacia-e-de-78-em-casos-leves-e-100-em-graves
09/01/2021 - Não é hora de sermos tão cientistas como estamos sendo agora https://g1.globo.com/sp/sao-paulo/video/nao-e-hora-de-sermos-tao-cientistas-como-estamos-sendo-agora-diz-secretario-de-saude-de-sp-9166405.ghtml
10/01/2021 - Dados da Coronavac relatados à Anvisa não estão claros, diz médico https://www.cnnbrasil.com.br/saude/2021/01/10/dados-da-coronavac-relatados-a-anvisa-nao-estao-claros-diz-medico
"O diretor do Laboratório de Imunologia do Incor, Jorge Kalil, reforçou que faltaram informações sobre a Coronavac nos dados divulgados à Anvisa"
12/01/2021 - New Brazil data shows disappointing 50,4% efficacy for China’s Coronavac vaccine [Novos dados do Brasil mostram eficácia decepcionante de 50,4% para a vacina CoronaVac da China] https://www.reuters.com/article/us-health-coronavirus-brazil-coronavirus/new-brazil-data-shows-disappointing-504-efficacy-for-chinas-coronavac-vaccine-idUSKBN29H2CE
13/01/2021 - Eficácia da Coronavac: 50,38%, 78% ou 100%? https://blogs.oglobo.globo.com/lauro-jardim/post/5038-78-ou-100.html
“De acordo com interlocutores que participaram tanto do anúncio de ontem como da semana passada, quem pressionou para que os dados de 78% e 100% fossem liberados foi João Dória.”
07/05/2021 - Covid-19: Doria toma primeira dose da vacina CoronaVac https://veja.abril.com.br/saude/covid-19-doria-toma-primeira-dose-da-vacina-coronavac/
04/06/2021 - Doria é vacinado com a segunda dose da CoronaVac em São Paulo https://noticias.uol.com.br/politica/ultimas-noticias/2021/06/04/doria-e-vacinado-com-a-segunda-dose-da-coronavac-em-sao-paulo.htm
15/07/2021 - Doria testa positivo para a Covid-19 pela 2ª vez https://www.correiobraziliense.com.br/politica/2021/07/4937833-doria-testa-positivo-para-covid-19-pela-segunda-vez.html
"Governador de São Paulo já havia sido diagnosticado com a doença no ano passado. Ele diz que, apesar da infecção, se sente bem, o que atribui ao fato de ter sido vacinado com duas doses da Coronavac"
06/08/2021 - CPI recebe investigação contra Doria por compra de máscara sem licitação https://www.conexaopoder.com.br/nacional/cpi-recebe-investigacao-contra-doria-por-compra-de-mascara-sem-licitacao/150827
"Empresa teria usado o nome de Alexandre Frota para vender máscaras ao governo de SP. Doria nega informação"
Renan Filho
(filho do Renan Calheiros)
25/07/2019 - Governador Renan Filho vai à China em busca de investimentos para o estado https://www.tnh1.com.br/videos/vid/governador-renan-filho-vai-a-china-em-busca-de-investimentos-para-o-estado/
20/03/2020 - Governadores do NE consultam China e pedem material para tratar covid-19 https://noticias.uol.com.br/saude/ultimas-noticias/redacao/2020/03/20/governadores-do-ne-consultam-china-e-pedem-material-para-tratar-covid-19.htm
5. Narrativas, restrições e proibições
17/12/2020 - STF decide que vacina contra a covid pode ser obrigatória, mas não forçada https://noticias.uol.com.br/saude/ultimas-noticias/redacao/2020/12/17/stf-julga-vacinacao-obrigatoria.htm?cmpid=copiaecola
"O STF (Supremo Tribunal Federal) decidiu, em julgamento hoje, que o Estado pode determinar a obrigatoriedade da vacinação contra a covid-19. Porém fica proibido o uso da força para exigir a vacinação, ainda que possam ser aplicadas restrições a direitos de quem recusar a imunização.
Dez ministros foram favoráveis a obrigatoriedade da vacinação, que poderá ser determinada pelo governo federal, estados ou municípios. As penalidades a quem não cumprir a obrigação deverão ser definidas em lei."
27/07/2021 - Saiba que países estão adotando 'passaporte da vacina' para suspender restrições https://www.cnnbrasil.com.br/internacional/2021/07/27/saiba-que-paises-estao-adotando-passaporte-da-vacina-para-suspender-restricoes
" - Israel - Uniao Europeia - Áustria - Dinamarca - Eslovênia - França - Grécia - Irlanda - Itália - Letônia - Lituânia - Luxemburgo - Holanda - Portugal - Japão - Coreia do sul"
18/06/2021 - O que é o passaporte da vacina que Bolsonaro quer vetar? https://noticias.uol.com.br/politica/ultimas-noticias/2021/06/18/uol-explica-o-que-e-o-passaporte-da-vacina-que-opoe-bolsonaro-e-damares.htm
"O Brasil poderá ter um certificado de imunização futuramente. Aprovado no Senado na semana passada, o "passaporte da vacina", como é chamado, prevê identificar pessoas vacinadas para que entrem em locais públicos ou privados com possíveis restrições."
6. Vacinas
Alegações iniciais
- CoronaVac, Oxford e Pfizer: veja diferenças entre as vacinas contra covid noticias.uol.com.br/saude/ultimas-noticias/redacao/2021/05/11/diferencas-vacinas-covid-brasil.htm
" - CoronaVac (Butantan/Sinovac - Chinesa) Com virus inativo 50,38% de eficácia 2 doses
-
Covishield - 'AstraZeneca' (Fiocruz/Astrazenica/Oxford - Britânica) Com virus não replicante 67% de eficácia 2 doses
-
ComiRNAty - 'Pfizer' (Pfizer - Americana / BioNTech - Alemã) Com RNA mensageiro 96% de eficácia 2 doses"
Riscos diretos
15/06/2021 - Trombose após vacinação com AstraZeneca: Quais os sintomas e como se deve atuar? https://www.istoedinheiro.com.br/trombose-apos-vacinacao-com-astrazeneca-quais-os-sintomas-e-como-se-deve-atuar/
"Agências europeias estão reticentes com a vacina da AstraZeneca. Ela chegou a ser desaconselhada a pessoas com idade inferior a 60 anos, e um alto funcionário da Agência Europeia de Medicamentos declarou que era melhor deixar de administrar a vacina deste laboratório em qualquer idade quando há alternativas disponíveis, devido aos relatos de trombose após a primeira dose, apesar de raros."
11/05/2021 - CoronaVac, Oxford e Pfizer: veja diferenças entre as vacinas contra covid https://noticias.uol.com.br/saude/ultimas-noticias/redacao/2021/05/11/diferencas-vacinas-covid-brasil.htm
"Na terça-feira (12), o Ministério da Saúde determinou a suspensão da aplicação da vacina de Oxford/AstraZeneca para gestantes e puérperas com comorbidades. A decisão segue recomendação da Anvisa, que apura a morte de uma grávida de 35 anos que tomou o imunizante e teve um AVC (acidente vascular cerebral)."
30/07/2021 - Pfizer representa o mesmo risco de trombose que a Astrazeneca, aponta levantamento https://panoramafarmaceutico.com.br/pfizer-representa-o-mesmo-risco-de-trombose-que-a-astrazeneca-aponta-levantamento/
7. CRIMES
Crimes da Pfizer
18/11/2020 Não listado no google - Os Crimes documentados da produtora de vacinas de Covid - Pfizer [INGLÊS] https://www.dmlawfirm.com/crimes-of-covid-vaccine-maker-pfizer-well-documented/
"A velocidade com que a vacina Covid da Pfizer foi produzida, a ausência de estudos em animais, testes de controle randomizados e outros testes e procedimentos padrão usuais para um novo medicamento são, no mínimo, preocupantes. Além disso, todos os fabricantes de vacinas Covid receberam imunidade legal para quaisquer ferimentos ou mortes que possam causar. Se essas vacinas são tão seguras quanto promovidas, por que seus fabricantes precisam de imunidade geral?"
"A Pfizer, uma empresa farmacêutica que parece ter ganhado na loteria para produzir a primeira vacina Covid-19, está atualmente lutando contra centenas de ações judiciais sobre o Zantac, um popular medicamento contra azia. Os processos da Zantac afirmam que a droga popular pode estar contaminada com uma substância cancerígena chamada N-nitrosodimetilamina (NDMA). Os processos Zantac são em aberto e em andamento, já que a farmacêutica está lutando contra eles; mas a Pfizer, sabemos, cometeu vários crimes ou transgressões pelos quais foi punida nos últimos anos. As falhas da empresa estão bem documentadas e vale a pena revisá-las neste momento crítico da história da humanidade, enquanto todos nós buscamos respostas."
A Pfizer recebeu a maior multa da história dos Estados Unidos como parte de um acordo judicial de US $ 2,3 bilhões com promotores federais por promover medicamentos erroneamente (Bextra, Celebrex) e pagar propinas a médicos complacentes. A Pfizer se confessou culpada de falsificar a marca do analgésico Bextra, promovendo o medicamento para usos para os quais não foi aprovado.
Na década de 1990, a Pfizer estava envolvida em válvulas cardíacas defeituosas que causaram a morte de mais de 100 pessoas. A Pfizer enganou deliberadamente os reguladores sobre os perigos. A empresa concordou em pagar US $ 10,75 milhões para acertar as acusações do departamento de justiça por enganar reguladores.
A Pfizer pagou mais de US $ 60 milhões para resolver um processo sobre o Rezulin, um medicamento para diabetes que causou a morte de pacientes de insuficiência hepática aguda.
No Reino Unido, a Pfizer foi multada em quase € 90 milhões por sobrecarregar o NHS, o Serviço Nacional de Saúde. A Pfizer cobrou do contribuinte um adicional de € 48 milhões por ano, pelo que deveria custar € 2 milhões por ano.
A Pfizer concordou em pagar US $ 430 milhões em 2004 para resolver acusações criminais de que havia subornado médicos para prescrever seu medicamento para epilepsia Neurontin para indicações para as quais não foi aprovado. Em 2011, um júri concluiu que a Pfizer cometeu fraude em sua comercialização do medicamento Neurontin. A Pfizer concordou em pagar $ 142,1 milhões para liquidar as despesas.
A Pfizer revelou que pagou quase 4.500 médicos e outros profissionais médicos cerca de US $ 20 milhões por falar em nome da Pfizer.
Em 2012, a Comissão de Valores Mobiliários dos Estados Unidos - anunciou que havia chegado a um acordo de US $ 45 milhões com a Pfizer para resolver acusações de que suas subsidiárias haviam subornado médicos e outros profissionais de saúde no exterior para aumentar as vendas no exterior.
A Pfizer foi processada em um tribunal federal dos Estados Unidos por usar crianças nigerianas como cobaias humanas, sem o consentimento dos pais das crianças. A Pfizer pagou US $ 75 milhões para entrar em acordo no tribunal nigeriano pelo uso de um antibiótico experimental, o Trovan, nas crianças. A empresa pagou um valor adicional não divulgado nos Estados Unidos para liquidar as despesas aqui. A Pfizer violou o direito internacional, incluindo a Convenção de Nuremberg estabelecida após a Segunda Guerra Mundial, devido aos experimentos nazistas em prisioneiros relutantes.
Em meio a críticas generalizadas de roubar os países pobres em busca de drogas, a Pfizer prometeu dar US $ 50 milhões para um medicamento para a AIDS para a África do Sul. Mais tarde, no entanto, a Pfizer falhou em honrar essa promessa.
- Pfizer contract leaked!
[Contrato da Pfizer vazado]
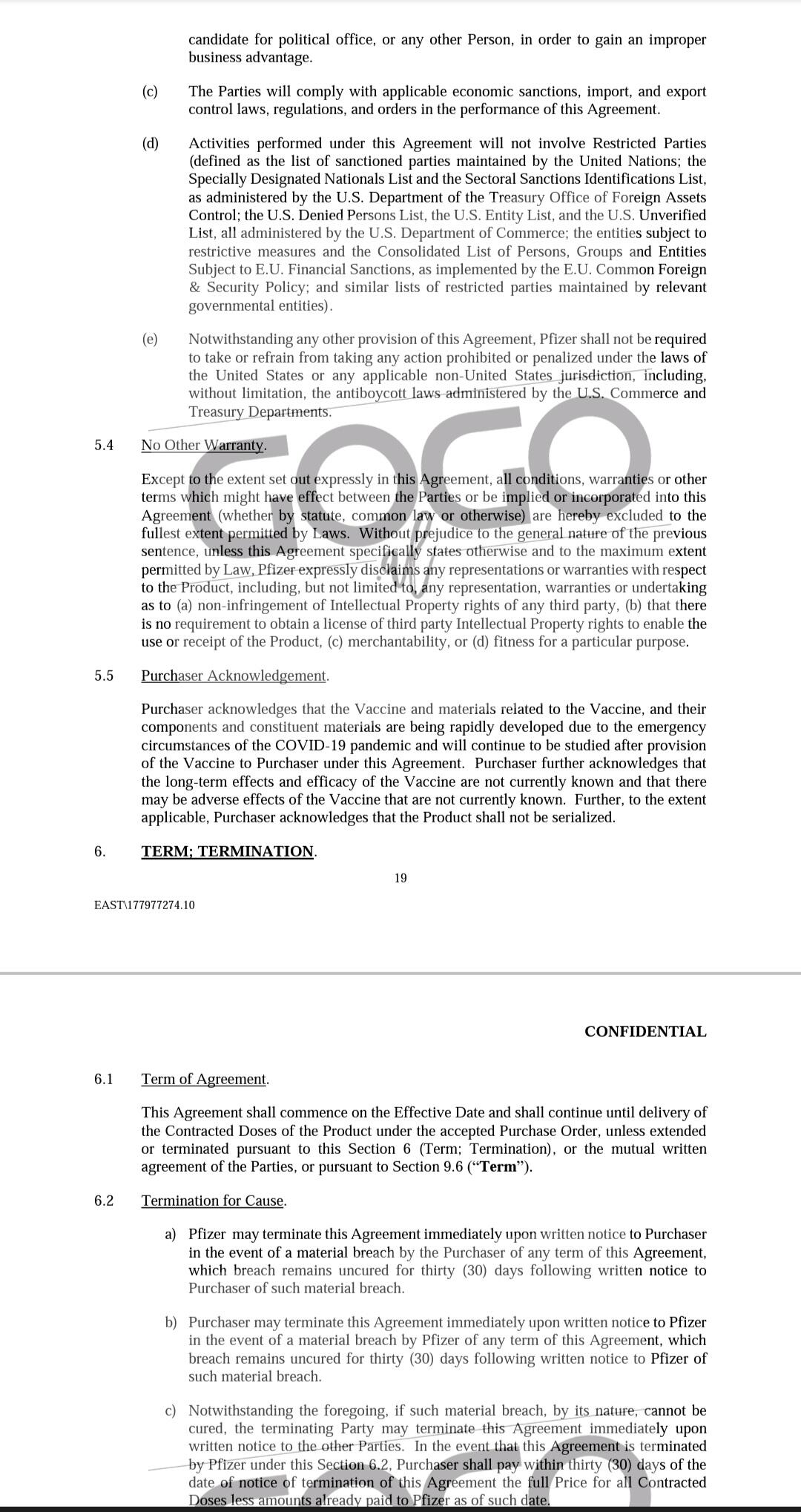 http://sanjeev.sabhlokcity.com/Misc/LEXO-KONTRATEN-E-PLOTE.pdf
http://sanjeev.sabhlokcity.com/Misc/LEXO-KONTRATEN-E-PLOTE.pdf
Segundo o contrato "o produto não deve ser serializado":
"5.5 Reconhecimento do comprador.
O Comprador reconhece que a Vacina e os materiais relacionados à Vacina, e seus componentes e materiais constituintes estão sendo desenvolvidos rapidamente devido às circunstâncias de emergência da pandemia de COVID-19 e continuarão a ser estudados após o fornecimento da Vacina ao Comprador nos termos deste Contrato. O Comprador reconhece ainda que os efeitos de longo prazo e eficácia da Vacina não são atualmente conhecidos e que pode haver efeitos adversos da Vacina que não são atualmente conhecidos. Além disso, na medida do aplicável, o Comprador reconhece que o Produto não deve ser serializado."
Crimes da AstraZeneca
21/06/2003 - AstraZeneca se declara culpada no esquema de médico de câncer https://www.nytimes.com/2003/06/21/business/astrazeneca-pleads-guilty-in-cancer-medicine-scheme.html
"A AstraZeneca, a grande empresa farmacêutica, se declarou culpada hoje de uma acusação de crime de fraude no sistema de saúde e concordou em pagar $ 355 milhões para resolver as acusações criminais e civis de que se envolveu em um esquema nacional para comercializar ilegalmente um medicamento contra o câncer de próstata.
O governo disse que os funcionários da empresa deram incentivos financeiros ilegais a cerca de 400 médicos em todo o país para persuadi-los a prescrever o medicamento Zoladex. Esses incentivos incluíram milhares de amostras grátis de Zoladex [...]"
27/04/2010 - Farmacêutica gigante AstraZeneca pagará US $ 520 milhões pelo marketing de medicamentos off-label https://www.justice.gov/opa/pr/pharmaceutical-giant-astrazeneca-pay-520-million-label-drug-marketing
"AstraZeneca LP e AstraZeneca Pharmaceuticals LP vão pagar $ 520 milhões para resolver as alegações de que a AstraZeneca comercializou ilegalmente o medicamento antipsicótico Seroquel para usos não aprovados como seguros e eficazes pela Food and Drug Administration (FDA), os Departamentos de Justiça e Saúde e Serviços Humanos A Equipe de Ação de Fiscalização de Fraudes em Saúde (HEAT) anunciou hoje. Esses usos não aprovados também são conhecidos como usos "off-label" porque não estão incluídos no rótulo do medicamento aprovado pela FDA."
- List of largest pharmaceutical settlements [Lista dos maiores acordos farmaceuticos] https://en.m.wikipedia.org/wiki/List_of_largest_pharmaceutical_settlements
8. CIENTISTAS
Especialistas Sérios
- Máscara Provoca Insuficiência Respiratória E Contaminação Microbiana… [Canal deletado] https://youtube.com/watch?v=eHu-pydSvDI
Não lembro mais a quem pertencia, mas provavelmente era de um médico falando do assunto. Creio ter sido do Dr. Paulo Sato, por essa temática ter sido abordada por ele, mas ao abrir o site aparece somente:
"Este vídeo foi removido por violar as diretrizes da comunidade do YouTube"
Dr. Paulo Sato
- USAR ou NÃO USAR a CUECA do seu governador no rosto https://fb.watch/7NPP_7rS5S/ https://www.facebook.com/AdoniasSoaresBR/videos/1347904292291481/ Adonias Soares entrevista ao Dr. Paulo Sato sobre as máscaras, em que é simulado o efeito da respiração prolongada das máscaras no organismo com o uso de águas de torneira, natural, gaseificada (com gás carbônico) e antioxidante, em que a com gás carbônico (PH 4 - Ácido) representa o organismo humano, e na prática representa lesão corporal e iniciação de doenças.
Dr. Kary Mullis
(Criador do teste PCR)
- PCR nas palavras do seu inventor - Dr. Kary Mullis (legendado) https://www.youtube.com/watch?v=W1O52uTygk8
"Qualquer um pode testar positivo para quase qualquer coisa com um teste de PCR, se você executá-lo por tempo suficiente… Com PCR, se voce fizer isso bem, você pode encontrar quase tudo em qualquer pessoa… Isso não te diz que você está doente."
- Kary Mullis DESTRUYE a Anthony Fauci lbry://@CapitalistChile#0/Kary-Mullis---Fauci#5
"Ele [...] não entende de medicina e não deveria estar onde está. A maioria dos que estão acima são só administrativos e não têm nem ideia do que ocorre aqui em baixo e essas pessoas tem uma agenda que não é a que gostaríamos que tivessem, dado que somos nós os que pagamos a eles para que cuidem da nossa saúde. Têm uma agenda pessoal."
Dra. Li-Meng Yan
- Dra. Li-Meng Yan: O vírus foi criado em laboratório com um objetivo: Causar dano. https://youtu.be/pSXp3CZnvOc
Dr. Joe Roseman
- Cientista Phd Dr Joe Roseman faz seríssimas advertencias sobre a picada https://youtu.be/0PIXVFqJ_h8
Dr. Robert Malone
- As vacinas podem estar causando ADE - Dr. Robert Malone https://odysee.com/@AkashaComunidad:f/Las_vacunas_pueden_estar_causando_ADE_magnificaci%C3%B3n_mediada_por:f lbry://@Información.#b/Drrm#9
Dr. Robert Malone, um dos três inventores da tecnologia de RNAm que se usa de forma farmacêutica. No vídeo fala sobre os efeitos de ADE (realce dependente de anticorpos) que estão ocorrendo com as vacinas. Nas palavras do Dr. Malone, já não é somente uma hipótese, mas baseada nos conhecimentos gerados nas provas e ensaios pré clínicos, com as vacinas contra o primeiro vírus da SARS.
Dr. Luc Montagnier
- Dr. Luc Montagnier, virologista, prêmio Nobel de medicina, um dos descobridores do vírus HIV, afirma: "a vacinação em massa está criando as novas variantes' (@medicospelavida , telegram)
Falsos Especialistas
-
Dr. Anthony Fauci - Imunologista
-
Dr. Atila Iamarino (nerdologia) - Microbiólogo
Atualmente propagandeia a pauta climática do COP30 (30th Conference Of Parties - UN [30ª Conferência das Partes - ONU]) que será no Brasil.
9. CASOS DOCUMENTADOS
13 de setembro de 2021 - 13/09/2021 - Carta aberta ao Ministro da Saúde por Arlene Ferrari Graf, mãe de Bruno Oscar Graf https://telegra.ph/Carta-aberta-ao-Ministro-da-Sa%C3%BAde-09-13
Também em: Gazeta do Povo
O texto de uma mãe discorrendo sobre o filho dela, Bruno Oscar Graf, ter ANTI-HEPARINA PF4 AUTO-IMUNE e ter vindo a falecer por reação à vacina.
11/05/2021 - Rio notifica morte de grávida vacinada com imunizante Oxford https://www.terra.com.br/noticias/coronavirus/rio-notifica-morte-de-gravida-vacinada-com-imunizante-oxford,415b9b0c49169427ac2f90ae3765c057e9suy3qn.html
"Vítima não apresentava histórico de doença circulatória nem sofria de nenhuma doença viral; relação será investigada"
13/08/2021 - Cruzeiro com 4.336 pessoas tem 27 contaminados com Covid-19 em Belize https://paranaportal.uol.com.br/geral/cruzeiro-com-4-336-pessoas-tem-27-contaminados-com-covid-19-em-belize/amp/
"Segundo um comunicado do Conselho de Turismo de Belize emitido na quarta-feira (11), 26 contaminados são da tripulação e um é passageiro. A maioria é assintomática e os 27 estão vacinados."
10. ALEGAÇÕES DIRETAS
Setembro de 2021 - 09/2021 - BOMBA: Ex-membro do Partido Comunista da China revela que o primeiro surto da Covid foi “intencional” https://terrabrasilnoticias.com/2021/09/bomba-ex-membro-do-partido-comunista-da-china-revela-que-o-primeiro-surto-da-covid-foi-intencional/
-
 @ cae03c48:2a7d6671
2025-06-05 15:01:20
@ cae03c48:2a7d6671
2025-06-05 15:01:20Bitcoin Magazine

MARA Announces Over $100 Million in Bitcoin Mined in May 2025Today, MARA Holdings, Inc. (NASDAQ: MARA) reported a record high month of bitcoin production in May 2025, mining 950 BTC worth over $100 million at the time of writing. A 35% increase from April and the highest monthly output since the April 2024 halving event. MARA did not sell any bitcoin in May.
JUST IN: MARA mined 950 #Bitcoin worth over $100 MILLION in May

They HODLed all of it
 pic.twitter.com/Z4v1zoEfga
pic.twitter.com/Z4v1zoEfga— Bitcoin Magazine (@BitcoinMagazine) June 3, 2025
“May was a record-breaking month for MARA with 282 blocks won, a 38% increase over April and a new monthly high,” said the Chairman and CEO of MARA Fred Thiel. “Our total bitcoin holdings surpassed 49,000 BTC during May and the 950 bitcoin produced were the most since the halving event in April 2024.”
The company mined 282 blocks during the month, a 38% rise over the previous month, and now holds 49,179 BTC, worth roughly $5.23 billion at the time of writing.
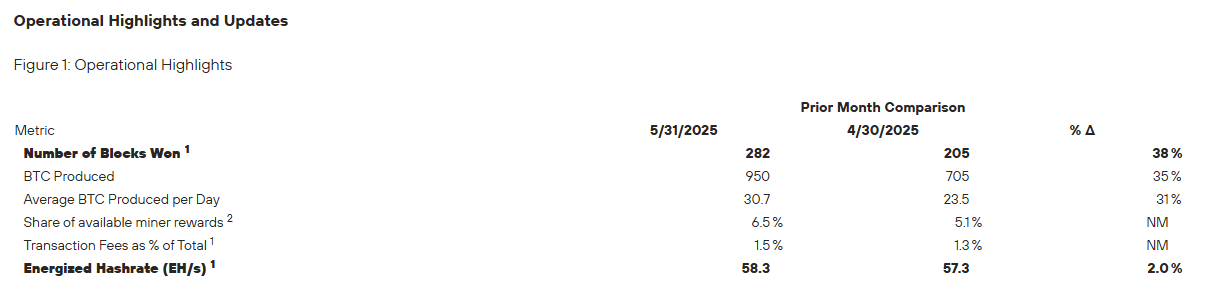
“Our fully integrated tech stack is a key differentiator, and MARA Pool is the only self-owned and operated mining pool among public miners, offering greater control and efficiency,” stated Thiel. “Operating our pool means no fees to external operators and retention of the full value of block rewards. Production in May also benefitted from block reward luck. Since launch, MARA Pool’s block reward luck has outperformed the network average by over 10%, contributing to our industry-leading block production.”
Operational efficiency also improved, with energized hashrate rising 2% from 57.3 EH/s to 58.3 EH/s. MARA’s average daily bitcoin production hit 30.7 BTC, which is 31% more than the last month from April.
“We remain laser-focused on transforming MARA into a vertically integrated digital energy and infrastructure company,” commented Thiel. “We believe this model gives us tighter operational control, improves cost-efficiency, and makes us more resilient to shifts in the broader economy.”
Earlier this month, on May 8, MARA released its first quarter 2025 earnings, posting 213.9 million dollars in revenue. A 30 percent increase over the same period last year. The company’s bitcoin holdings surged 174 percent year over year, rising from 17,320 BTC to 47,531 BTC as of March 31, with an estimated value of 3.9 billion dollars at the time. In Q1, MARA mined 2,286 BTC and acquired an additional 340 BTC. Operational performance also strengthened, with energized hashrate nearly doubling from 27.8 EH/s to 54.3 EH/s, and cost per petahash per day improving by 25 percent.
This post MARA Announces Over $100 Million in Bitcoin Mined in May 2025 first appeared on Bitcoin Magazine and is written by Oscar Zarraga Perez.
-
 @ 20e7c953:3b8bcb21
2025-06-05 10:46:07
@ 20e7c953:3b8bcb21
2025-06-05 10:46:0721… That number means something. A reminder that limits create value - both in Bitcoin and in life.
Every June 21st, skaters around the world remind us that freedom is something you make yourself - one push at a time only constrained by your own limitations.
This year in Vientiane, we’re proud to support one of the few real skate spots in Laos. A place built and held together by skaters for skaters.
Expect around 50 locals - from young kids to older heads - showing up not just to skate, but to hold space for each other. No ego, no filters, just boards, fun and respect.
Bircoiners have lots to learn from these communities on this regard. Go skate and you'll find out.
SnF
Laostr
Skateboardingisfun
Skate4Fun
Skatestr
-
 @ fbf0e434:e1be6a39
2025-06-05 14:08:24
@ fbf0e434:e1be6a39
2025-06-05 14:08:24Hackathon 概要
ETHBratislava Hackathon Vol.2 汇聚 54 名开发者并审核通过 11 个项目,成为以太坊社区的重要盛事。此次黑客马拉松在斯洛伐克技术大学举办,参与者可免费参与 ETHBratislava 大会,这一安排助力开发者探索区块链技术的前沿进展。
项目在解决以太坊可扩展性与互操作性问题上成果显著,尤其在 “World Computer” 赛道表现突出。“Zircuit Restaking Track” 赛道也带来重要创新,聚焦通过 AI 驱动的 zk rollups 技术提升安全性与扩展性。“European Stablecoin EURØP Challenge” 则致力于开发欧元背书的稳定币,推动欧洲监管数字货币概念落地。
参与者不仅获得资深导师指导、与行业领袖建立连接的机会,现场更有招聘方挖掘技术人才。活动在兼具庆祝与社交属性的派对中落幕。总计 4,000 欧元奖金的设置,营造了开发者之间竞争与合作并存的创新氛围。ETHBratislava Vol.2 成功孵化出影响以太坊未来的创新构想,同时强化了社区联结。
Hackathon 获奖者
World Computer 奖项获奖者
此类别着重于利用以太坊能力的面向消费者的应用程序。开发者创建了解决方案,旨在增强包容性、金融工具和教育平台。获奖者包括:
- Zhar: 该去中心化平台使用AI和以太坊区块链来管理、执行和激励使用智能合约和代币的链上挑战。
- Ledger Lens: 一个Web应用程序,促进对以太坊多层生态系统的可视化和分析,强调代币流动和跨链桥使用等指标。
现实世界代币化奖项获奖者
此类别集中于在欧洲利用EUR锚定的稳定币EURØP构建效用。项目目标是在此数字货币之上部署初步技术增强。
- dEST: 一个去中心化平台,利用NFTs和智能合约来促进无中介的代币化房地产交易。
- EnergyHub: 一个提供去中心化平台以货币化多余绿色能源并通过智能合约和用户友好的仪表板实现能源捐赠的应用程序。
Restaking 奖项获奖者
此类别鼓励团队在Zircuit生态系统内的AI驱动zkEVM上进行构建,着重于支持AI增强安全性和创新zk rollup技术的项目。
- RestakerX: 一个仪表板应用程序,设计用于跟踪Zircuit网络上的数字资产,提供算法建议以最大化收益。
有关所有项目的更多详细信息和此次黑客马拉松中展示的创新理念的进一步见解,请访问 ETHBratislava Hackathon页面。
关于组织者
Ethereum Bratislava
Ethereum Bratislava 是中欧和东欧地区区块链和技术领域的一个重要社区,致力于推进以太坊的开发和整合。由一支专家团队支持,该组织在增强以太坊在中欧和东欧地区的可扩展性和安全性的项目中作出了重大贡献。积极参与社区活动和教育活动强调了他们在区块链领域促进技术创新和知识共享的承诺。Ethereum Bratislava 继续支持技术改进和生态系统增长,旨在增强以太坊的能力和跨各行业的采用。
-
 @ b1ddb4d7:471244e7
2025-06-04 11:01:29
@ b1ddb4d7:471244e7
2025-06-04 11:01:29Bitcoin FilmFest (BFF25) returns to Warsaw for its third edition, blending independent cinema—from feature films and commercials to AI-driven experimental visuals—with education and entertainment.
Hundreds of attendees from around the world will gather for three days of screenings, discussions, workshops, and networking at the iconic Kinoteka Cinema (PKiN), the same venue that hosted the festival’s first two editions in March 2023 and April 2024.
This year’s festival, themed “Beyond the Frame,” introduces new dimensions to its program, including an extra day on May 22 to celebrate Bitcoin Pizza Day, the first real-world bitcoin transaction, with what promises to be one of Europe’s largest commemorations of this milestone.
BFF25 bridges independent film, culture, and technology, with a bold focus on decentralized storytelling and creative expression. As a community-driven cultural experience with a slightly rebellious spirit, Bitcoin FilmFest goes beyond movies, yet cinema remains at its heart.
Here’s a sneak peek at the lineup, specially curated for movie buffs:
 Generative Cinema – A special slot with exclusive shorts and a thematic debate on the intersection of AI and filmmaking. Featured titles include, for example: BREAK FREE, SATOSHI: THE CREATION OF BITCOIN, STRANGE CURRENCIES, and BITCOIN IS THE MYCELIUM OF MONEY, exploring financial independence, traps of the fiat system, and a better future built on sound money.
Generative Cinema – A special slot with exclusive shorts and a thematic debate on the intersection of AI and filmmaking. Featured titles include, for example: BREAK FREE, SATOSHI: THE CREATION OF BITCOIN, STRANGE CURRENCIES, and BITCOIN IS THE MYCELIUM OF MONEY, exploring financial independence, traps of the fiat system, and a better future built on sound money. Upcoming Productions Preview – A bit over an hour-long block of unreleased pilots and works-in-progress. Attendees will get exclusive first looks at projects like FINDING HOME (a travel-meets-personal-journey series), PARALLEL SPACES (a story about alternative communities), and THE LEGEND OF LANDI (a mysterious narrative).
Upcoming Productions Preview – A bit over an hour-long block of unreleased pilots and works-in-progress. Attendees will get exclusive first looks at projects like FINDING HOME (a travel-meets-personal-journey series), PARALLEL SPACES (a story about alternative communities), and THE LEGEND OF LANDI (a mysterious narrative). Freedom-Focused Ads & Campaigns – Unique screenings of video commercials, animations, and visual projects, culminating in “The PoWies” (Proof of Work-ies)—the first ever awards show honoring the best Bitcoin-only awareness campaigns.
Freedom-Focused Ads & Campaigns – Unique screenings of video commercials, animations, and visual projects, culminating in “The PoWies” (Proof of Work-ies)—the first ever awards show honoring the best Bitcoin-only awareness campaigns.To get an idea of what might come up at the event, here, you can preview 6 selected ads combined into two 2 videos:
 Open Pitch Competition – A chance for filmmakers to present fresh ideas and unfinished projects to an audience of a dedicated jury, movie fans and potential collaborators. This competitive block isn’t just entertaining—it’s a real opportunity for creators to secure funding and partnerships.
Open Pitch Competition – A chance for filmmakers to present fresh ideas and unfinished projects to an audience of a dedicated jury, movie fans and potential collaborators. This competitive block isn’t just entertaining—it’s a real opportunity for creators to secure funding and partnerships. Golden Rabbit Awards: A lively gala honoring films from the festival’s Official Selection, with awards in categories like Best Feature, Best Story, Best Short, and Audience Choice.
Golden Rabbit Awards: A lively gala honoring films from the festival’s Official Selection, with awards in categories like Best Feature, Best Story, Best Short, and Audience Choice.BFF25 Main Screenings
Sample titles from BFF25’s Official Selection:
 REVOLUCIÓN BITCOIN – A documentary by Juan Pablo, making its first screening outside the Spanish-speaking world in Warsaw this May. Three years of important work, 80 powerful minutes to experience. The film explores Bitcoin’s impact across Argentina, Colombia, Mexico, El Salvador, and Spain through around 40 diverse perspectives. Screening in Spanish with English subtitles, followed by a Q&A with the director.
REVOLUCIÓN BITCOIN – A documentary by Juan Pablo, making its first screening outside the Spanish-speaking world in Warsaw this May. Three years of important work, 80 powerful minutes to experience. The film explores Bitcoin’s impact across Argentina, Colombia, Mexico, El Salvador, and Spain through around 40 diverse perspectives. Screening in Spanish with English subtitles, followed by a Q&A with the director. UNBANKABLE – Luke Willms’ directorial debut, drawing from his multicultural roots and his father’s pioneering HIV/AIDS research. An investigative documentary based on Luke’s journeys through seven African countries, diving into financial experiments and innovations—from mobile money and digital lending to Bitcoin—raising smart questions and offering potential lessons for the West. Its May appearance at BFF25 marks its largest European event to date, following festival screenings and nominations across multiple continents over the past year.
UNBANKABLE – Luke Willms’ directorial debut, drawing from his multicultural roots and his father’s pioneering HIV/AIDS research. An investigative documentary based on Luke’s journeys through seven African countries, diving into financial experiments and innovations—from mobile money and digital lending to Bitcoin—raising smart questions and offering potential lessons for the West. Its May appearance at BFF25 marks its largest European event to date, following festival screenings and nominations across multiple continents over the past year. HOTEL BITCOIN – A Spanish comedy directed by Manuel Sanabria and Carlos “Pocho” Villaverde. Four friends, 4,000 bitcoins , and one laptop spark a chaotic adventure of parties, love, crime, and a dash of madness. Exploring sound money, value, and relationships through a twisting plot. The film premiered at the Tarazona and Moncayo Comedy Film Festival in August 2024. Its Warsaw screening at BFF25 (in Spanish with English subtitles) marks its first public showing outside the Spanish-speaking world.
HOTEL BITCOIN – A Spanish comedy directed by Manuel Sanabria and Carlos “Pocho” Villaverde. Four friends, 4,000 bitcoins , and one laptop spark a chaotic adventure of parties, love, crime, and a dash of madness. Exploring sound money, value, and relationships through a twisting plot. The film premiered at the Tarazona and Moncayo Comedy Film Festival in August 2024. Its Warsaw screening at BFF25 (in Spanish with English subtitles) marks its first public showing outside the Spanish-speaking world.Check out trailers for this year’s BFF25 and past editions on YouTube.
Tickets & Info:
- Detailed program and tickets are available at bitcoinfilmfest.com/bff25.
- Stay updated via the festival’s official channels (links provided on the website).
- Use ‘LN-NEWS’ to get 10% of tickets