-
 @ df478568:2a951e67
2025-06-05 23:34:01
@ df478568:2a951e67
2025-06-05 23:34:01About 156,000 blocks ago, I went to a Taco Shop for a bitcoin meetup. I asked my favorite question, “Do you accept bitcoin?”
“Yes," he said as he handed me a Toast Terminal with a BTCpayServer QR code.
 ]
]Awesome!
12,960 blocks later, I took my dad to the taco shop. We ordered food. I asked my favorite question once again.
“Uh…Yeah, but I don't know how to work the machine.”
"Dough!🤦"
It's been a problem in the past, but now lightning payments are about to be ubiquitous. Steak N Shake is taking bitcoin using Speed Wallet and Block is implementing bitcoin payments by 2026 in all legal jurisdictions. I have tested both of these so you don't have to. Just kidding. I geek out on this stuff, but both work great. You can pay with your sats by scanning a screen on a QR code. The employees don't need to be bitcoin lightning network experts. You can just pay as easy as a credit card.
There were 35,000 people at the bitcoin conference, and 4,187 transactions were made. It was a world record. Wait, I thought they said there could only be 7 transactions per second! No, not anymore. Now we can use bitcoin for shopping. I can pay for tacos at taco trucks.

How You Can Accept Bitcoin At Your Business
Coinos is a simple bitcoin point of sale information that acts like a cash register. Bitcoin is peer-to-peer electronic cash. Coinos is a cash register and you should treat it as such. If you make a few hundred thousand sats at the end of the night, you should sweep the bitcoin into your own wallet.. You can use Aqua, AlbyHub, Bull Bitcoin wallet, or whatever your favorite lightning enabled wallet is to withdraw. You'll need a password. Do not lose this. I have tried the automatic withdraws, but it did not work for me. I'm no concerned because this is not a wallet I intend to keep a lot of sats in for a long time.
Here is my coinos payment terminal.
https://coinos.io/ZapthisBlog/receive
I made the QR code with libreqr.com/

Now I have an online bitcoin cash register. The Bitcoiners know how to pay for stuff with sats. They will be proud to show you too. If you're nerdy, you can use all the cool kid tools now, but we will just focus on the lightning address. Anyone can send you sats with a lightning address with just a QR code.
At the end of the night, you cash out to your own wallet. Again, this assumes you have an Aqua Wallet or any other lightning enabled wallet, but all it takes to accept bitcoin at your brick and mortar store is to create an account with Coinos and print out a QR code. It's a quick and easy way to start accepting bitcoin even if you don't expect many clients to shop with sats.
Tips
This is not just a cash register. Employees can also make their own Coinos wallet and receive tips from bitcoiners. Anyone can accept payments using this system. Your kids could use it to sell lemonade for sats. You are only limited by your imagination. When will you begin accepting bitcoin payments? It is easier than ever. You do not need to train employees. You do not need to be in the store. Bitcoin is peer-to-peer electronic cash so you can give it away like cash. I don't know what the tax rules on cash are. You need to verify that with your own jurisdiction. This is not financial or tax advice. This is for informational purposes only.
Remember, this is a custodial wallet. Not your keys not your bitcoin. Don't keep more sats than you are willing to lose on custodial wallets. Sweep your wallet early and often. Loss of funds is possible. There is a small fee for liquidity management too. Do your own research.
-
 @ 374ee93a:36623347
2025-06-05 22:42:00
@ 374ee93a:36623347
2025-06-05 22:42:00Chef's notes
Start your day the self sovereign way
Details
- ⏲️ Prep time: 10 mins
- 🍳 Cook time: 15 mins
- 🍽️ Servings: 4
Ingredients
- 1lb Jar Bottled Rhubarb https://jimblesjumble.netlify.app/item/a0c35618722834ac714d0a47058a2adc76ee7485a6b74f5da5f9eb2d3fb5d879
- 1pt Homemade Custard (3/4pt cream, 3 large eggs, 100g honey, 1/2 tbspn vanilla extract)
- 4 Handfuls Granola
- 1 Node https://plebeian.market/products/huxley@nostrplebs.com/start-9-node-y22zfjp8x6
Directions
- Whisk together the cream, eggs, honey and vanilla
- Chill overnight or serve warm with 1/4 jar of stewed rhubarb and a large handful of granola per person
- Consolidate some UTXOs on your node
- Have a Good Morning
-
 @ 58537364:705b4b85
2025-06-05 15:55:12
@ 58537364:705b4b85
2025-06-05 15:55:12อารมณ์ คือ โลก - โลก คือ อารมณ์ อารมณ์ ในโลกปัจจุบันรวมอยู่ที่ วัตถุนิยม อารมณ์ จึงเป็นปัจจัยแห่งเหตุการณ์ทุกอย่างในโลก
…. “ เดี๋ยวนี้คําว่า “อารมณ์” ในภาษาไทยนั้น หมายถึงความรู้สึกในใจมากกว่า; เช่น พื้นเพของจิตใจในขณะนั้นเป็นอย่างไร, เรียกว่าอารมณ์ของเขาเป็นอย่างไร, อารมณ์กําลังดี อารมณ์กําลังไม่ดี, นี่ คําว่าอารมณ์ในภาษาไทยใช้กันไปเสียอย่างนี้ ; มันคนละเรื่องกับในภาษาบาลี ซึ่งคําว่า “อารมณ์” หมายถึง สิ่งที่จะเข้ามากระทบ ตา หู จมูก ลิ้น กาย ใจ.
…. ถ้ากระทบแล้วเกิดความรู้สึกอย่างไร งุ่นง่านอยู่ในใจ อันนั้นไม่ได้เรียกว่าอารมณ์; อันนั้นก็เรียกว่ากิเลสอย่างอื่น เช่น เรียกว่าตัณหาบ้าง อุปาทานบ้าง; ถ้าจัดเป็นพวกขันธ์ ก็เรียกว่า เวทนาขันธ์บ้าง สัญญาขันธ์บ้าง สังขารขันธ์บ้าง; ถ้าเป็นความคิดที่งุ่นง่านก็เรียกว่า “สังขารขันธ์” ทั้งนั้น ดังนั้น เราจะต้องถือเอาคําว่าอารมณ์ในบาลีมาเป็นหลัก …. คําว่า อารมณ์ ที่จะเข้าใจกันง่ายๆ ก็หมายความว่า รูป เสียง กลิ่น รส โผฏฐัพพะ ที่จะมากระทบ ตา หู จมูก ลิ้น กาย นี้ ๕ อย่าง แล้วก็ความรู้สึกเก่าแก่ที่จะมาผุดขึ้นในใจอีก เรียกว่า ธัมมารมณ์ ที่จะมากระทบใจในปัจจุบันนี้ นี้ก็เป็นอันหนึ่ง เลยได้เป็นอารมณ์ ๖. อารมณ์กระทบ ตา หู จมูก ลิ้น กาย ๕ อย่างข้างนอกนี้ก็สําคัญไปพวกหนึ่ง ที่ปรุงขึ้นภายในสําหรับกระทบใจโดยไม่ต้องอาศัย ตา หู จมูก ลิ้น กาย ใจ เลย ในเวลานั้นก็ยังมีอยู่นี้เรียกว่าธัมมารมณ์ นี้ก็ยิ่งสําคัญ: แต่ว่ารวมกันแล้วก็เรียกว่า อารมณ์ ได้ด้วยกันทั้งนั้น แปลว่า สิ่งที่จะมากระทบกับ ตา หู จมูก ลิ้น กาย ใจ นั่นเอง
…. นี้ ดูให้ละเอียดตามตัวหนังสือ คําว่า “อารมณ์” แปลว่า ที่หน่วงบ้าง แปลว่า ที่ยินดีบ้าง, มันมีความหมายละเอียดมาก. ถ้าถือเอาความหมายอย่างคนที่มีตัวตนเป็นหลัก ธรรมะในฝ่ายฮินดูหรือฝ่ายพรหมณ์เขาก็จะพูดว่า สําหรับจิตหรืออาตมันเข้าไปจับฉวยเอา. แต่ถ้าพูดอย่างภาษาชาวพุทธพูดอย่างนั้นไม่ได้ เพราะไม่มีจิตไม่มีอาตมันชนิดนั้น แล้วจิตนี้ก็เพิ่งเกิดขึ้นหลังอารมณ์กระทบแล้ว; เลยต้องพูดตามพระบาลีที่ว่า อาศัยตาด้วย อาศัยรูปด้วย ย่อมเกิดจักษุวิญญาณ; ตาอาศัยกับรูปคืออารมณ์นั้นได้แล้วจึงจะเกิดจักษุวิญญาณ วิญญาณหรือจิตนี้เกิดทีหลัง
…. ฉะนั้น จึงไม่พูดว่า อารมณ์นี้เป็นสิ่งสําหรับจิตหรือตัวตนเข้าไปจับฉวยยึดเอา; ถ้าพูดอย่างนั้นมันก็จะเป็นฮินดูหรือพราหมณ์ไป คือมีตัวตนไป. พูดอย่างพุทธไม่มีตัวตน ทุกอย่างไม่ใช่ตัวตน เป็นสักว่าธาตุ, ได้การปรุงแต่งที่เหมาะแล้วมันก็ปรุงแต่งเป็นสิ่งใหม่ขึ้นมา ในนั้นอาจจะมีความรู้สึกโง่ไปว่าเป็นตัวเราก็ได้
…. ฉะนั้น คําว่าอารมณ์ ถ้าถือตามหลักในทางพุทธศาสนา ก็แปลว่า สิ่งที่อาศัยกันกับจิต จะเรียกว่าเป็นที่หน่วงของจิตมันก็ยังได้: ถ้าเข้าใจผิดมันก็ผิดได้: เรียกว่าสิ่งที่อาศัยกับอายตนะ แล้วก็เกิดเป็นความรู้สึกเป็นจิตขึ้นมา จิตกําลังหน่วงสิ่งนั้นเป็นอารมณ์ก็ได้ แต่จะให้เป็นตัวตนนั้นไม่ได้
…. โดยพยัญชนะก็มีอยู่อย่างนี้ ตัวพยัญชนะก็ยังกํากวม อารมฺมณํ หรือที่มาจาก อาลมฺพนํ ก็แปลว่า ที่หน่วงของจิต. ถ้าจะถือว่ามาจาก รม ที่แปลว่า ยินดี ก็แปลว่า มันเป็นสิ่งที่หลงใหลยินดีของจิต อย่างนี้ก็ยังได้อีก
…. แต่ขอให้รู้จักจากภายในดีกว่าที่จะมารู้จักจากตัวหนังสือ เมื่อตากระทบรูป เมื่อหูกระทบเสียง เป็นต้น มันเกิดขึ้นในใจ, แล้วสังเกตเอาที่นั่นก็แล้วกัน ว่ารูปที่มากระทบตานั้นมันคืออะไร? เสียงที่มากระทบหูนั้นมันคืออะไร? จะค่อยเข้าใจแจ่มแจ้งขึ้นทีละน้อยๆ ว่าอารมณ์นั้นคืออะไร? แต่ให้เข้าใจไว้ทีหนึ่งก่อนว่าสิ่งที่เรียกว่าอารมณ์ๆที่มากระทบนี้ มันยังไม่ดีไม่ชั่ว ยังไม่จัดเป็นสิ่งดีสิ่งชั่ว มันต้องผสมปรุงแต่งเป็นความคิดอย่างนั้นอย่างนี้เสียก่อน จึงจะจัดเป็นดีเป็นชั่ว อารมณ์ล้วนๆยังไม่ดีไม่ชั่ว จะได้รู้จักป้องกัน อย่าให้เป็นไปในทางชั่ว, ให้เป็นไปแต่ในทางดีได้ตามปรารถนา
…. นี้เรียกว่าโดยพยัญชนะ โดยตัวหนังสือ คําว่า “อารมณ์” แปลว่า เป็นที่ยินดีแห่งจิต, เป็นที่ยึดหน่วงแห่งจิต; โดยเฉพาะภาษาอภิธรรมแล้วก็ใช้คําว่า “เป็นที่หน่วงเอาของจิต”, คือจิตย่อมหน่วงสิ่งใดสิ่งหนึ่งเป็นอารมณ์ แปลคําว่าอารมณ์บ้าง, อาลัมพนะ แปลว่า เป็นที่หน่วงเอา.
…. เดี๋ยวนี้เราเรียนพุทธศาสนาไม่ใช่เรามาเรียนหนังสือบาลี, เราจะเรียนพระธรรมคําสอนของพระพุทธเจ้า เราก็ต้องดูสิ่งที่เรียกว่าอารมณ์ โดยหลักของธรรมชาติที่ปรุงแต่งกันอยู่ในใจดีกว่า; ก็อย่างพระบาลีที่ได้ว่ามาแล้วข้างต้นว่า จกฺขุญฺจ ปฏิจฺจ รูเป จ อุปฺปชฺชติ จกฺขุวิญฺญาณํ = เพราะอาศัยตาด้วย รูปด้วย ย่อมบังเกิดจักษุวิญญาณ ติณฺณํ ธมฺมานํ สงฺคติ ผสฺโส - การประจวบกันของ ๓ สิ่งนี้เรียกว่า “ผัสสะ”, ผสฺสปจฺจยา เวทนา = เพราะผัสสะเป็นปัจจัยจึงเกิดเวทนา, อย่างนี้เรื่อยไปจนเกิดทุกข์ จนเกิดความทุกข์, นี้เรียกว่าโดยธรรมชาติ
…. สิ่งที่เรียกว่าอารมณ์มีอยู่โดยธรรมชาติที่จะเข้ามาอาศัยกันกับตาข้างใน ที่มีอยู่ในตัวคน. แล้วจะเกิดจักษุวิญญาณ เป็นต้น ขึ้นในตัวคน; จะเกิด ผัสสะ เวทนา ตัณหา อุปาทาน ภพ ชาติ ขึ้นในตัวคน; นี้โดยธรรมชาติ พระพุทธเจ้าท่านบันดาลอะไรไม่ได้ : ธรรมชาติเป็นอยู่อย่างนี้ แต่ท่านรู้เรื่องนี้ท่านจึงนํามาสอนว่า ธรรมชาติมันมีอยู่อย่างนี้ เราจะต้องเข้าใจให้ถูกต้อง โดยที่จะป้องกันความทุกข์ไม่ให้เกิดขึ้นมาได้, หรือถ้าเกิดขึ้นมาได้ก็จะดับเสียได้
…. เราควรจะรู้จักอารมณ์ในฐานะที่เป็นธรรมชาติอันหนึ่ง ที่มีอยู่ตามธรรมชาติ แล้วที่จะเข้ามาทําเรื่องทําราวขึ้นในจิตใจของคนเราให้เกิดปัญหายุ่งยากนี้ให้ดีๆ นี้เรียกว่ารู้จักอารมณ์จากธรรมชาติโดยตรงอย่างนี้ ดีกว่าที่จะรู้จักตามตัวหนังสือ, ดีกว่าที่จะรู้จักตามคําบอกเล่าบางอย่างบางประการที่มันไม่มีประโยชน์อะไร. รู้จักตามคําบอกเล่าก็รู้จักตามที่พระพุทธเจ้าท่านตรัสดีกว่า แต่แล้วยังไม่รู้จักตัวจริง จนกว่าจะมารู้จักจากที่เมื่ออารมณ์มากระทบตา หู จมูก ลิ้น กาย ใจ เข้าจริงๆ : นั่นจึงจะรู้จักอารมณ์ รู้จักผลที่เกิดขึ้นจากการกระทบของอารมณ์, รู้จักต่อไปตามลําดับ จนแก้ปัญหาต่างๆ ได้
…. นี่ ขอร้องให้รู้จักสิ่งที่เรียกว่า อารมณ์ ในฐานะที่เป็นธรรมชาติอันหนึ่ง ที่มีอยู่ตามธรรมชาติ ที่จะเข้ามากระทบอายตนะภายใน คือ กระทบ ตา หู จมูก ลิ้น กาย ใจ แล้วมีเรื่องมีราวมีปัญหา
อารมณ์ คือ โลก - โลก คือ อารมณ์ …. “ ที่นี้จะให้ดูต่อไปอีก ว่าโดยข้อเท็จจริงที่เป็นอยู่แล้ว อารมณ์นั้นคืออะไร? ถ้าจะพูดโดยข้อเท็จจริงหรือตามสถานการณ์ที่เป็นอยู่จริงในชีวิตของคนเรา อารมณ์มันก็คือ “โลก” นั่นเอง. เดี๋ยวนี้เราไม่รู้จักโลกในฐานะอย่างนี้, เราไปเข้าใจความหมายของคําว่าโลกแคบไปบ้าง หรือว่าเขวไปบ้าง.
…. ถ้าจะรู้ตามหลักพระพุทธศาสนาแล้ว โลกทั้งหมดก็คือสิ่งที่จะมาปรากฏแก่ ตา หู จมูก ลิ้น กาย ใจ ของเรา, เรามีเพียง ๖ อย่าง, แล้วมันก็ ปรากฏได้เพียง ๖ ทาง, มากกว่านั้นมันปรากฏไม่ได้ ดังนั้น โลกก็คือสิ่งที่จะมาปรากฏแก่ ตา หู จมูก ลิ้น กาย ใจ ๖ อย่างของเรา. “โลก” ก็คือ รูป เสียง กลิ่น รส โผฏฐัพพะ ธัมมารมณ์ ๖ ประการเท่านั้น, ไม่มีอะไรมากไปกว่านั้น
…. ฉะนั้น รูป เสียง กลิ่น รส โผฏฐัพพะ ธัมมารมณ์ แต่ละอย่าง ๆ ก็คือ โลกในแต่ละแง่ละมุม นั่นเอง, ที่เป็น รูป เสียง กลิ่น รส โผฏฐัพพะ ก็อยู่ข้างนอก จะเรียกว่าอยู่ข้างนอกก็ได้, ที่เป็นอารมณ์เกิดขึ้นในใจ ปรุงขึ้นในใจก็เรียกว่าโลกข้างในก็ได้ แต่มันก็เป็นโลกอยู่นั่นแหละ เพราะมันเป็นสิ่งที่จิตจะต้องรู้สึก จิตรู้สึกก็เรียกว่าโลกสําหรับจิต ตา หู จมูก ลิ้น กาย รู้สึก ก็เรียกว่าโลกสำหรับ ตา หู จมูก ลิ้น กาย. นี้ขอให้มองให้เห็นชัดตามพระพุทธประสงค์ว่า โลก ก็คือ อารมณ์, อารมณ์ ก็คือ โลก.
…. แต่ทีนี้ พระพุทธเจ้าท่านมองลึกกว่านั้น ท่านตรัสถึงข้อที่ว่า ถ้ามันมาเกิดเป็นปัญหาแก่เราเมื่อไรจึงจะเรียกว่า “มันมี” พอมันมาเป็นปัญหาแก่เราเมื่อไรก็เรียกว่า “เป็นทุกข์”; เพราะว่าเราได้ไปจับฉวยยึดถือเอาตามประสาตามวิสัยของคนที่ไม่รู้จักโลก ถ้าพูดว่าไม่รู้จักโลกแล้วคนก็มักจะไม่ยอมรับ เพราะว่าเขาจะพูดว่าเขารู้จักโลกดี. ยิ่งพวกฝรั่งสมัยนี้ นักวิทยาศาสตร์ปราดเปรื่องนั้น เขาจะไม่ยอมรับว่าเขาไม่รู้จักโลก. แต่ถ้าพูดตามหลักพุทธศาสนาแล้วก็จะพูดได้ว่ายังไม่รู้จักโลกเลย เป็นคนตาบอดยิ่งกว่าตาบอด; เพราะว่าฝรั่งเหล่านั้นรู้จักโลกแต่ในแง่สําหรับจะยึดมั่นถือมั่นเป็น “ตัวกู ของกู” จะครองโลกจะอะไร เอาประโยชน์ทุกอย่าง; เขารู้จักโลกในแง่นี้ อย่างนี้พุทธบริษัทไม่เรียกว่า “รู้จักโลก”; แต่ถือว่าเป็นคนตาบอดต่อโลก, หลงยึดมั่นถือมั่นในโลก. เพราะว่าคนเหล่านั้นไม่รู้จักโลกโดยความเป็นอารมณ์ ๖ ประการ คือ รูป เสียง กลิ่นรส โผฏฐัพพะ ธัมมารมณ์, แล้วเป็น “มายา” คือ เอาจริงไม่ได้ เป็นของชั่วคราวๆ หลอกให้เกิดความรู้สึกยึดมั่นถือมั่น
…. นี้เรารู้จัก เราไม่ไปหลงยึดมั่นถือมั่นกับมัน นี้จึงเรียกว่า “คนที่รู้จักโลก” ไปตามหลักของพุทธศาสนา, ฉะนั้น จึงไม่ยึดมั่นถือมั่นสิ่งใดโดยความเป็นตัวตน หรือโดยความเป็นของตน, เรียกว่าเป็นผู้รู้จักอารมณ์ ๖ ประการนั้นก็คือรู้จักโลกทั้งปวง, แล้วก็ไม่หลงไปในโลกในแง่ใดแง่หนึ่ง นี้เรียกว่า อารมณ์ ก็คือ โลก นั่นเอง ในความหมายที่ลึกที่สุดของพระพุทธสาสนา ไม่ใช่โลกก้อนดิน, ไม่ใช่โลกก้อนกลมๆ นี้. แต่มันหมายถึงคุณค่าอะไรที่มันมีอยู่ในโลกกลมๆ นี้ ที่จะเข้ามามาทําให้เกิดปัญหา ที่ตา ที่หู ที่จมูก ที่ลิ้น ที่กาย ที่ใจ ของคน. นั่นแหละคือตัวร้ายกาจของสิ่งที่เรียกว่า โลก เราจะต้องรู้จักในส่วนนี้ให้เพียงพอ
อารมณ์ในโลกปัจจุบันมารวมที่วัตถุนิยม …. ทีนี้ ดูอีกแง่หนึ่งก็โดยปัญหาที่กําลังมีอยู่ อารมณ์ในโลกนี้ในฐานะที่มันเป็นตัวปัญหาที่กําลังมีอยู่ มันมารวมอยู่ที่คําว่า “วัตถุนิยม”: หมายความว่า ตา หู จมูก ลิ้น กาย ใจ นี้ มันเป็นฝ่ายชนะ ไปหลงใหลในอารมณ์ รูป เสียง กลิ่น รส โผฏฐัพพะ ฯลฯ, แล้วก็เกิดนิยมหลงใหลในวัตถุเหล่านั้น จนเกิดความคิดใหม่ๆ, ปรุงแต่งไปในทางที่จะให้หลงใหลในโลกยิ่งขึ้นๆ, ความเจริญก้าวหน้า ในโลกสมัยนี้เป็นไปแต่ในทางอย่างนี้ ฉะนั้น จึงไกลความสงบ, ไกลสันติภาพ ไกลอะไรออกไปทุกที. การที่มนุษย์ที่มีปัญญาในโลกสมัยนี้ โดยเฉพาะฝรั่งที่ก้าวหน้านั้นเขาก็จัดโลกไปแต่ในแง่ของวัตถุมากขึ้นๆ: มันก็ไกลจากสันติภาพ ไกลจากความสงบสุขยิ่งขึ้นทุกที
…. ความสะดวกสบายที่ทําให้เกิดขึ้นมาได้นั้น ไม่ได้ช่วยส่งเสริมเกิดสันติภาพ; แต่มันช่วยให้เกิดความหลงในโลกนั้นเองมากขึ้น แล้วก็ช่วยให้หลงใหลใน “ตัวกู ของกู”, ยึดมั่นถือมั่นเห็นแก่ตัวมากขึ้น รวมกันแล้วมันไม่มีทางที่จะเกิดสันติภาพหรือสันติสุขในโลกได้เลย, จึงกลายเป็นความหลอกลวงเหลือประมาณ โลกจึงกลายเป็นความหลอกลวง, หรือสิ่งที่หลอกลวงเหลือประมาณใน เวลานี้ เราเรียกกันว่า ติดบ่วง หรือว่า ติดเหยื่อของวัตถุนิยม. คําพูดทั้งหมดนี้ ล้วนแต่เป็นการแสดงให้เห็นว่า อารมณ์นี้คืออะไร สิ่งที่เรียกว่าอารมณ์นั้น คือตัวโลกที่กําลังหลอกลวงเราอยู่ทุกวันอย่างยิ่ง โดยเฉพาะในปัจจุบันนี้เป็นวัตถุนิยม นี้คืออารมณ์”
พุทธทาสภิกขุ ที่มา : ธรรมบรรยายภาคมาฆบูชา ครั้งที่ ๗ หัวข้อเรื่อง “อารมณ์ คือ ปัจจัยแห่งเหตุการณ์ทุกอย่างในโลก” เมื่อวันที่ ๑๖ กุมภาพันธ์ ๒๕๑๗ จากหนังสือชุดธรรมโฆษณ์ เล่มชื่อว่า “ก ข ก กา ของการศึกษาพุทธศาสนา”
หมายเหตุ
“อารมณ์ ” ในทางพุทธศาสนา มี ๖ คือ... * ๑. รูปะ = รูป, สิ่งที่เห็น หรือ วัณณะ คือ สี * ๒. สัททะ = เสียง * ๓. คันธะ = กลิ่น * ๔. รสะ = รส * ๕. โผฏฐัพพะ = สัมผัสทางกาย * ๖. ธรรมารมณ์ = สิ่งที่ใจนึกคิด, อารมณ์ที่เกิดกับใจ
…. ทั้ง ๖ อย่างนี้ เป็นสิ่งสำหรับให้จิตยึดหน่วง เรียกอีกอย่างว่า "อายตนะภานนอก" ก็ได้
“อายตนะภายใน ๖” คือ ที่เชื่อมต่อให้เกิดความรู้, แดนต่อความรู้ฝ่ายภายใน มี * ๖ อย่าง คือ... * ๑. จักษุ - ตา * ๒. โสตะ - หู * ๓. ฆานะ - จมูก * ๔. ชิวหา - ลิ้น * ๕. กาย - กาย * ๖. มโน - ใจ
… หรือจะเรียกอีกอย่างว่า “อินทรีย์ ๖” ก็ได้ เพราะเป็นใหญ่ในหน้าที่ของตนแต่ละอย่าง เช่น จักษุ เป็นเจ้าการ(เป็นใหญ่)ในการเห็น เป็นต้น
ท. ส. ปัญญาวุฑโฒ – รวบรวม.
-
 @ 3eab247c:1d80aeed
2025-06-05 08:51:39
@ 3eab247c:1d80aeed
2025-06-05 08:51:39Global Metrics
Here are the top stats from the last period:
- Total Bitcoin-accepting merchants: 15,306 → 16,284
- Recently verified (1y): 7,540 → 7,803 (the rest of our dataset is slowly rotting; help us before it's too late!)
- Avg. days since last verification: 398 → 405 (more mappers, please)
- Merchants boosted: 22 (for a total of 4,325 days, someone is feeling generous)
- Comments posted: 34
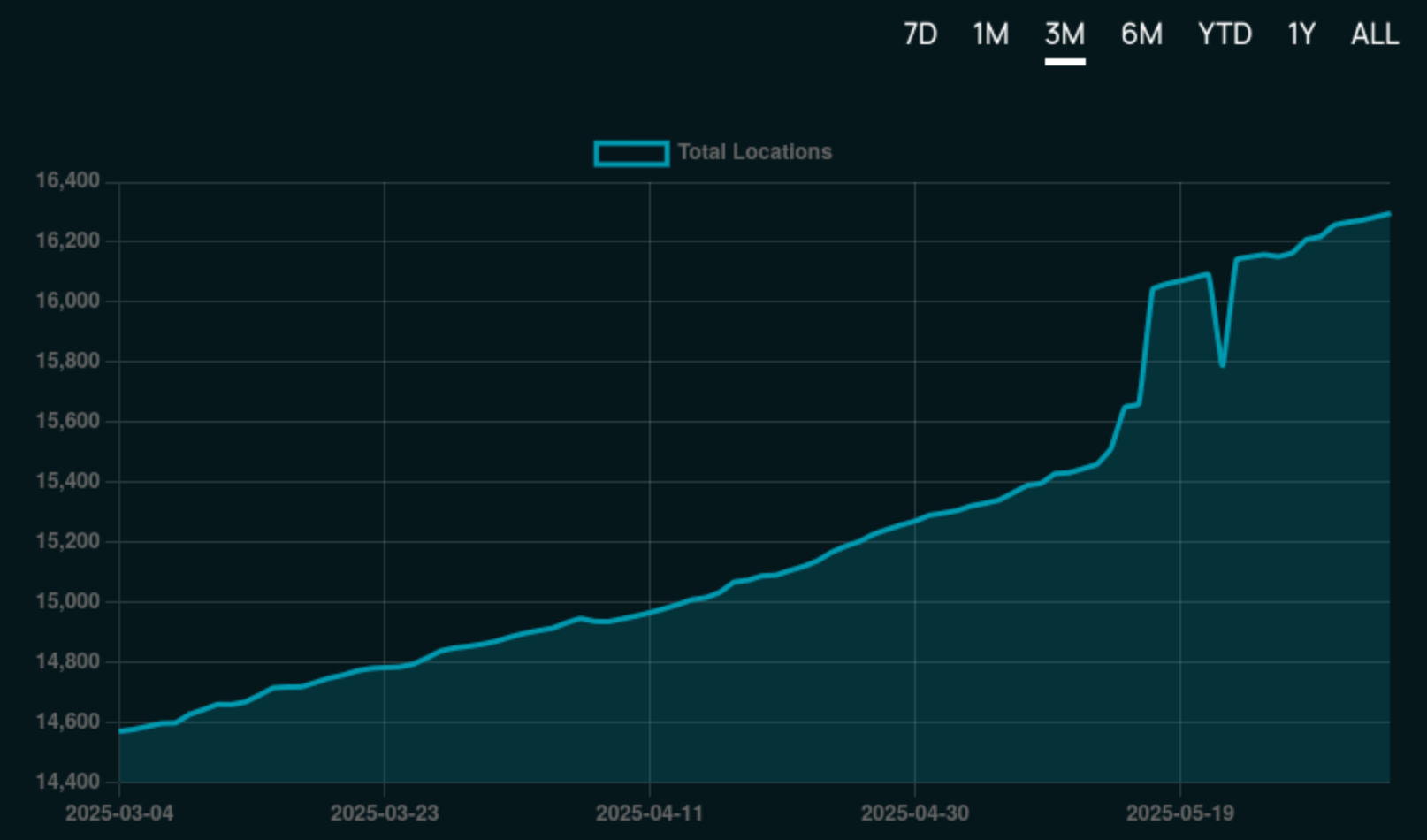
Find current stats over at the 👉 BTC Map Dashboard.
Merchant Adoption
Steak n’ Shake
The US 🇺🇸 is a massive country, yet its BTC Map footprint has been lagging relative to other countries ... that is until now!

In what came as a nice surprise to our Shadowy Supertaggers 🫠, the Steak ’n Shake chain began accepting Bitcoin payments across hundreds of its locations nationwide (with some international locations too).
According to CoinDesk, the rollout has been smooth, with users reporting seamless transactions powered by Speed.
This marks a significant step towards broader Bitcoin adoption in the US. Now to drop the capital gains tax on cheesburgers!
SPAR Switzerland
In other chain/franchise adoption news, the first SPAR supermarket in Switzerland 🇨🇭 to begin accepting Bitcoin was this one in Zug. It was quickly followed by this one in Rossrüti and this one in Kreuzlingen, in what is believed to be part of a wider roll-out plan within the country powered by DFX's Open CryptoPay.
That said, we believe the OG SPAR crown goes to SPAR City in Arnhem Bitcoin City!
New Features
Merchant Comments in the Web App
Web App users are now on par with Android users in that they can both see and make comments on merchants.
This is powered by our tweaked API that enables anyone to make a comment as long as they pass the satswall fee of 500 sats. This helps keep spam manageable and ensure quality comments.
And just in case you were wondering what the number count was on the merchant pins - yep, they're comments!
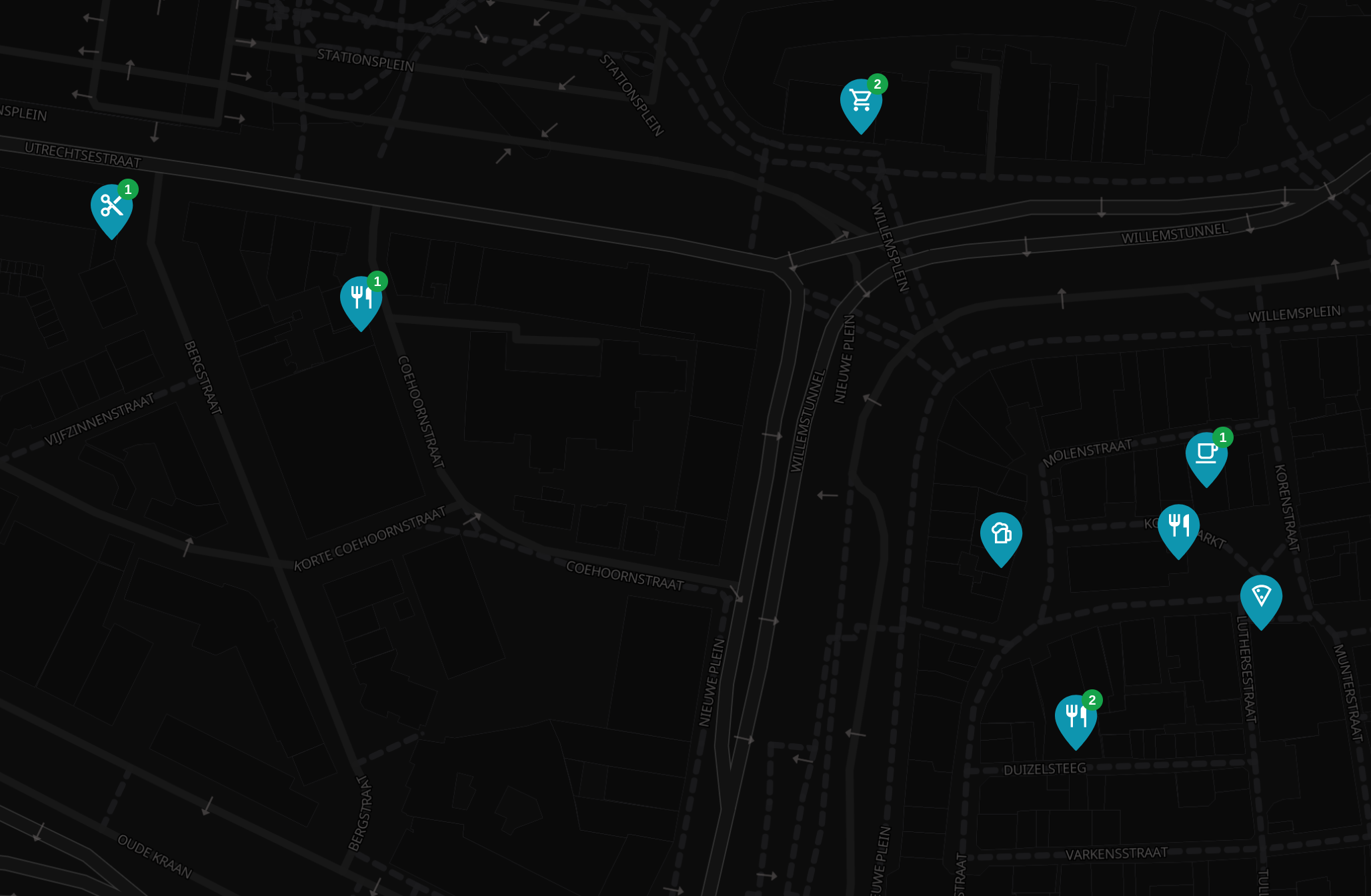
Here is an 👉 Example merchant page with comments.
Merchant Page Design Tweaks
To support the now trio of actions (Verify, Boost & Comment) on the merchant page, we've re-jigged the design a little to make things a little clearer.
What do you think?
Technical
Codebase Refactoring
Thanks to Hannes’s contributions, we’ve made progress in cleaning-up the Web App's codebase and completing long overdue maintenance. Whilst often thankless tasks, these caretaking activities help immensely with long-term maintainability enabling us to confidently build new features.
Auth System Upgrades
The old auth system was held together with duct tape and prayers, and we’re working on a more robust authentication system to support future public API access. Updates include:
- Password hashing
- Bearer token support
- Improved security practices
More enhancements are in progress and we'll update you in the next blog post.
Better API Documentation
Instead of relying on tribal knowledge, we're finally getting around to writing actual docs (with the help/hindrance of LLMs). The "move fast, break everything" era is over; now we move slightly slower and break slightly less. Progress!
Database Improvements
We use SQLite, which works well but it requires careful handling in async Rust environments. So now we're untangling this mess to avoid accidental blocking queries (and the ensuing dumpster fires).
Backup System Enhancements
BTC Map data comes in three layers of fragility:
- Merchants (backed up by OS - the big boys handle this)
- Non-OSM stuff (areas, users, etc. - currently stored on a napkin)
- External systems (Lightning node, submission tickets - pray to Satoshi)
We're now forcing two core members to backup everything, because redundancy is good.
Credits
Thanks to everyone who directly contributed to the project this period:
- Comino
- descubrebitcoin
- Hannes
- Igor Bubelov
- Nathan Day
- Rockedf
- Saunter
- SiriusBig
- vv01f
Support Us
There are many ways in which you can support us:
-
Become a Shadowy Supertagger and help maintain your local area or pitch-in with the never-ending global effort.
-
Consider a zapping this note or make a donation to the to the project here.
-
 @ 2cde0e02:180a96b9
2025-06-05 21:45:00
@ 2cde0e02:180a96b9
2025-06-05 21:45:00日本の姫
https://stacker.news/items/998335
-
 @ 21335073:a244b1ad
2025-05-09 13:56:57
@ 21335073:a244b1ad
2025-05-09 13:56:57Someone asked for my thoughts, so I’ll share them thoughtfully. I’m not here to dictate how to promote Nostr—I’m still learning about it myself. While I’m not new to Nostr, freedom tech is a newer space for me. I’m skilled at advocating for topics I deeply understand, but freedom tech isn’t my expertise, so take my words with a grain of salt. Nothing I say is set in stone.
Those who need Nostr the most are the ones most vulnerable to censorship on other platforms right now. Reaching them requires real-time awareness of global issues and the dynamic relationships between governments and tech providers, which can shift suddenly. Effective Nostr promoters must grasp this and adapt quickly.
The best messengers are people from or closely tied to these at-risk regions—those who truly understand the local political and cultural dynamics. They can connect with those in need when tensions rise. Ideal promoters are rational, trustworthy, passionate about Nostr, but above all, dedicated to amplifying people’s voices when it matters most.
Forget influencers, corporate-backed figures, or traditional online PR—it comes off as inauthentic, corny, desperate and forced. Nostr’s promotion should be grassroots and organic, driven by a few passionate individuals who believe in Nostr and the communities they serve.
The idea that “people won’t join Nostr due to lack of reach” is nonsense. Everyone knows X’s “reach” is mostly with bots. If humans want real conversations, Nostr is the place. X is great for propaganda, but Nostr is for the authentic voices of the people.
Those spreading Nostr must be so passionate they’re willing to onboard others, which is time-consuming but rewarding for the right person. They’ll need to make Nostr and onboarding a core part of who they are. I see no issue with that level of dedication. I’ve been known to get that way myself at times. It’s fun for some folks.
With love, I suggest not adding Bitcoin promotion with Nostr outreach. Zaps already integrate that element naturally. (Still promote within the Bitcoin ecosystem, but this is about reaching vulnerable voices who needed Nostr yesterday.)
To promote Nostr, forget conventional strategies. “Influencers” aren’t the answer. “Influencers” are not the future. A trusted local community member has real influence—reach them. Connect with people seeking Nostr’s benefits but lacking the technical language to express it. This means some in the Nostr community might need to step outside of the Bitcoin bubble, which is uncomfortable but necessary. Thank you in advance to those who are willing to do that.
I don’t know who is paid to promote Nostr, if anyone. This piece isn’t shade. But it’s exhausting to see innocent voices globally silenced on corporate platforms like X while Nostr exists. Last night, I wondered: how many more voices must be censored before the Nostr community gets uncomfortable and thinks creatively to reach the vulnerable?
A warning: the global need for censorship-resistant social media is undeniable. If Nostr doesn’t make itself known, something else will fill that void. Let’s start this conversation.
-
 @ 3eba5ef4:751f23ae
2025-06-06 02:07:27
@ 3eba5ef4:751f23ae
2025-06-06 02:07:27Crypto Insights
Solving Sybil Attacks on Bitcoin Libre Relay Nodes — Are Social Solutions Better than Technical Ones?
Peter Todd posted that proponents of transaction "filtering" have started Sybil attacking Libre Relay nodes by running nodes with their "Garbageman" fork. These malicious nodes pretend to support NODE_LIBRE_RELAY, but secretly drop certain transactions that would be relayed by real Libre Relay nodes. He also highlighted the complexity of existing defenses and proposed a new angle: rather than relying on technical solutions, he encourages people to manually peer with nodes operated by people they personally know, arguing that human relationships can sometimes evaluate honesty more reliably than code.
Toward a Unified Identity Lookup Standard to Improve Lightning Payments
Bitcoin developer Aviv Bar-el introduced a new proposal — Well-Known Bitcoin Identity Endpoint — that aims to simplify wallet lookups for users’ Bitcoin addresses and identity data via a standardized HTTPS interface, thereby improving both the UX and security of Lightning and on-chain payments.
A Commit/Reveal Mechanism to Strengthen Bitcoin Against Quantum Threats
Tadge Dryja proposed a soft fork for Bitcoin to defend against quantum attacks, based on a variant of the commit/reveal Fawkescoin mechanism. While similar to Tim Ruffing’s earlier proposal, it includes key differences:
- It does not use encryption, instead relying on smaller, hash-based commitments, and describes activation as a soft fork.
- It only applies to outputs where public keys or scripts haven't been revealed — like pubkey hash or script hash outputs. It also works with Taproot, but must be spent via the script path, as the key-path is no longer quantum-secure.
- What to do about already-exposed public keys is a separate issue — this proposal is compatible with both "burning the coins" and "letting them be stolen."
Countdown to the Quantum Crisis: Is Bitcoin Ready?
A recent report from Chaincode Labs analyzes the threat of cryptographically relevant quantum computers (CRQC), and the technical, economic, and governance challenges Bitcoin faces in preparing. Their key conclusions:
- Timeline Assessment: CRQC capable of breaking Bitcoin's elliptic curve cryptography may emerge between 2030 and 2035.
- Scope of Vulnerable Funds: An estimated 20–50% of circulating BTC (4M–10M coins) may be vulnerable.
- Long-range attacks target inherently vulnerable script types (P2PK, P2MS, P2TR) and addresses with previously exposed public keys (via address reuse), allowing attackers unbounded time to derive private keys from public information already available on the blockchain.
- Short-range attacks, which affect all Bitcoin script types, exploit the vulnerability window between transaction broadcast and confirmation (or shortly thereafter) when public keys are temporarily exposed, requiring attackers to act within a timeframe of minutes to hours.
- Action Strategy: A dual-track approach is recommended:
- Short-term contingency: minimal but functional protections within ~2 years.
- Full-featured solutions: comprehensive research and fully developed defenses within ~7 years.
This strategy balances immediate needs with rigorous development to ensure Bitcoin can adapt, regardless of CRQC progress.
Enforcing Arbitrary Constraints on Bitcoin Transactions with zkSNARKs
Current methods for constraining Bitcoin transactions fall short on privacy or programmability. This research proposes a new zkSNARK-based design to impose arbitrary constraints on Bitcoin transactions while preserving some information privacy. By bypassing Bitcoin Script’s non-Turing-completeness, the approach allows unbounded constraints—constraints that repeat a certain operation an unbounded number of times. Read the paper.
First Cross-Chain Bridge Between Bitcoin and Cardano Is Live
A trust-minimized bridge from Bitcoin to Cardano has launched using the Cardinal protocol, enabling Ordinals to move between the two chains. The Cardinal protocol is based on BitVMX and facilitates asset movement without compromising ownership or security.
Its core mechanism is a committee-based validation model under a 1-out-of-n honest security model — meaning even if all but one validator is malicious, the system remains secure. This approach enhances decentralization and censorship resistance for cross-chain asset transfers.
Thunderbolt Protocol: Redefining Bitcoin Smart Contracts with UTXO Bundling and OP_CAT
Nubit’s Thunderbolt is seen as one of the most significant technical upgrades to Bitcoin in a decade, whose overall observation resembles “Lightning Network 2.0.” Rather than relying on Layer 2 networks or bridges, Thunderbolt upgrades the Bitcoin base layer via soft fork to enhance scalability, performance, and programmability:
- Throughput: Uses UTXO Bundling to optimize traditional transaction processing.
- Programmability: Reintroduces and extends OP_CAT.
- Asset protocols: Integrates Goldinals standard — a zk-proof and state-commitment-based asset issuance framework.
- Unlike rollups, Plasma, sidechains, or bridges, Thunderbolt scales directly on the main chain. With BitVisa, it enables decentralized identity and credentials, supporting transaction compression, smart contracts, asset standard integration, and on-chain transaction matching — all on Bitcoin main chain.
Bitcoin 2025 Conference Recap: Politicians Applaud, Stablecoins Spotlighted, DeFi Absent
This year’s Bitcoin 2025 conference in Las Vegas gathered major political figures and corporate leaders. U.S. Vice President JD Vance strongly endorsed crypto and positioned Bitcoin as a strategic asset in U.S.–China competition. He also stated that stablecoins won’t undermine the U.S. dollar, but could actually amplify America’s economic strength.
White House “Crypto Czar” David Sacks delivered a major policy announcement, hinting that under Trump’s executive order, the U.S. has a legal framework to acquire more Bitcoin for strategic reserves.
In addition, stablecoin regulation and crypto market reform were hot topics. Ardoido, the company controls over 60% of the stablecoin market, claimed “All the traditional financial firms will create stablecoins that will be offered to their existing customers.” Meanwhile, Tether emphasized its focus on underserved global populations excluded from the existing banking system.
A conference recap also noted that, unlike the 2022 and 2023 summits, this year’s event was dominated by Bitcoin maximalists, Ordinals creators, mining capitalists, and regulatory lobbyists — no longer DeFi builders, DAO operators, or Layer 2 scaling advocates. Developers from Ethereum and Solana ecosystems were notably absent. This may signal:
- The conference’s heavy political and sovereignty-driven tone made it less suitable for the tech-centric narratives favored by these developers.
- There may be a growing ideological and narrative rift between Web3 builders and the Bitcoin camp.
Top Reads on Blockchain and Beyond
Rethinking Governance After the Sui Attack: Decentralization, Procedural Legitimacy, and the Plurality of Blockchain Values
Following a major hack of Cetus, the largest DEX in the Sui ecosystem, the Sui network executed a protocol-level asset freeze and recovery. While this was an effective technical response, it also triggered criticism and debate around core blockchain principles such as censorship resistance and decentralization.
The author of this article questioned the absolutist stance that views decentralization as the highest—and sole—value. The author argues that most rational individuals would prefer “living in a society where decentralization is a supreme value but coercive force is allowed when someone infringes on another’s property,” over “a society where decentralization is the only supreme value, and thus coercive force is never permitted under any circumstances.”
In addition, the author also expressed disappointment at Sui’s “paternalistic” governance — particularly how validators acted during the incident. Sui uses a delegated proof-of-stake (dPoS) system, where token holders delegate their voting power to validators. This means individuals lose their direct say. But blockchain governance could be more individual-friendly and flexible. For instance, in Cosmos’ governance model, for certain specific proposal, users still can override their delegations and vote independently, more favorable than Sui’s model.
Beyond the debate on decentralization and governance, the article also proposes an alternative perspective: what matters most is establishing procedural legitimacy that aligns with the system’s vision. Different blockchain projects pursue different goals. For Sui, the core mission is to enable assets to be reliably defined and interact seamlessly on-chain. Therefore, judging Sui through the lens of other blockchains’ values or paradigms is misguided. In exceptional cases, prioritizing asset recovery and ecosystem stability over strict adherence to censorship resistance aligns more closely with Sui’s long-term vision. Whether Sui had chosen to not to censor related transactions or to intervene in the Cetus case, as long as the action follows a legitimate process, either decision is justifiable.
TEE-Based Private Proof Delegation
The PSE research and development team has built a system based on Trusted Execution Environments (TEE) using Intel TDX for secure zero-knowledge proof (ZKP) delegation. This system enables clients to privately outsource large proving tasks without leaking inputs. Unlike mobile-native proving constrained by hardware limits, TEE-based approaches support significantly larger statements today—and will scale further as proof systems improve. As a hardware-backed solution, TEEs remain compatible with future advancements in software (e.g., faster proof systems, more efficient implementations) and won't be invalidated by them, as long as the trust model is acceptable.
AI and Identity: Proof of Humanity in a World of Agents, Bots, and Deepfakes
We are living in a time where AI—including agents, bots, and deepfakes—is fundamentally reshaping the internet. As AI continues to evolve, identity verification on the web is becoming more crucial than ever. A recent a16z podcast explores the idea of “Proof of Human”—the challenge of verifying human identity online, diving into why it matters, common questions, and how such systems work under the hood.
-
 @ df67f9a7:2d4fc200
2025-06-05 19:52:32
@ df67f9a7:2d4fc200
2025-06-05 19:52:32Nostr is NOT a social network. Nostr is a network of interconnected social apps. And, since any app is a social app, Nostr is for every app.
ONLY Nostr incentivizes inter-connectivity between independent apps, simply by respecting sovereignty at the protocol layer. For end users, sovereignty means that the content they post “to Nostr” will never be owned by the apps that they use. For businesses building apps on Nostr, sovereignty means that every app actually benefits by other apps being on the network. Because sovereignty is respected, users are retained for longer and independent apps thrive far longer on Nostr than on the legacy “black box” social networks.
Social apps thrive on Nostr
Nostr integration provides these benefits for every app :
- Unrestrained access for any app, to all public and private data “on Nostr”. No fees or licenses for harvesting user data from the network.
- Unburdened from liability, when collecting user data with any app. When sending “to Nostr”, end users retain custody of user data while apps never loose access.
- Unlimited free market of search engines and feed algos. Users and brands can create, use, and share any algos or custom feeds. Grow your audience on your own terms.
- Universal open network for all apps. Build any kind of app for any audience, on the same network as other apps for other audiences. Discover new trends from user data.
- Unregulated tech platform. Build your own app and use it as you wish. No gate keepers. No code review.
Sovereignty is good for business.
Regardless of the network size, a Nostr integrated app can grow its user base MUCH faster and with greater independence BECAUSE of the sovereignty respecting protocol. While end users may retain custody of their identities and data on the network, it’s the apps that determine which data is, or is not, sent to the network. Respect for sovereignty IS the killer feature that ONLY the Nostr protocol provides for apps and for end users.
Because Nostr is permissionless for any app to integrate :
- end users will always have a free market of apps choose from
- apps are free to integrate only as much as benefits their business model.
- apps gain access to more novel data as new apps bring new users to the network.
Because data on Nostr is managed by end users and available to all apps :
- User data looses exclusivity and the demand shifts toward novel insights and information derived from these data.
- Apps are freed from having to be “data pirates”, and can focus on establishing a trusted user base, providing valuable services to satisfied customers, informed by the abundance of user data.
- Apps are incentivized to offload data onto the network, establishing a new paradigm for interconnectivity, where independence is NOT at stake as the network grows.
- New markets spring up to support users with self custody of their data, driven by the reality that apps can have full access without assuming responsibility.
- The market for search and algo tools opens up for independent apps and end users to discover and interact freely with each other.
- The ad based “attention economy” slowly transforms to a value based consumer economy, where the end user is the customer rather than the product being sold.
Even while privacy is respected
Sometimes sovereignty is at odds with privacy, but Nostr allows all parties to win while both are protected.
- For end users sending sensetive data "to Nostr", privacy is assured by encrypting it with their own private keys and/or sending it to private (auth required) relays of their choosing.
- For apps handling private IP or business data, any traditional “black box” infrastructure can be used in the back end to manitain isolation from Nostr.
This means apps and end users remain in control of their own private data, without requiring “big social” as trust provider or data reseller. To access a user's private data, client apps (even search engines, running locally) only need explicit permission from the end user to retrieve or decrypt from Nostr relays. Public data, on the other hand, is freely available for any app or search engine to harvest from any Nostr relay. In either case, user data on the Nostr network is always accessible to client apps, without additional restrictions or fees.
Nostr is for every app.
Adding social to any app makes it a better app. Add reviews for products or services. Add commenting or direct messaging. Share or collaborate on content creation. Nostr integration is straightforward and incremental for any app.
Nostr doesn't define your app's business model ... Nostr 10X's it!
Here's how :
- Start with your own business and app design. Add Nosrr login.
- Discover what "kinds" of user data already exists "on Nostr" that your app can ingest and make use of.
- Decide which "kinds" of data would benefit your business, your users, and the network, if sent "to Nostr".
- Implement Nostr integration for data kinds and add webs of trust tools for recommendation and discovery.
- Verify your app is sovereignty respecting in how it handles private data and implements Nostr NIPs.
- Engage with existing users, and onboard new users from your app, to earn their trust and patronage over Nostr.
For more info and assistance, contact our team of Nostr integration experts.
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ ac8bb9b0:70278acc
2025-06-05 18:12:29
@ ac8bb9b0:70278acc
2025-06-05 18:12:29Details
- ⏲️ Prep time: 15 min
- 🍳 Cook time: 20 min
- 🍽️ Servings: 12
Ingredients
- 1 and 1/2 cups (345g) mashed bananas (about 4 medium or 3 large ripe bananas)
- 1/3 cup (113g) honey
- 1 large egg
- 1/4 cup (56g) coconut oil, melted
- 1 teaspoon pure vanilla extract
- 1 cup (130g) whole wheat flour
- 1/2 cup (41g) natural unsweetened cocoa powder
- 1 teaspoon baking powder
- 1 teaspoon baking soda
- 1/2 teaspoon salt
- 1 cup (180g) semi-sweet or dark chocolate chips
Directions
- Preheat oven to 425°F (218°C). Spray a 12-count muffin pan with nonstick spray or line with cupcake liners. Set aside.
- In a medium bowl, mash the bananas up using a fork.* Try to mash up any large lumps. Once mashed, whisk in the honey, egg, coconut oil, and vanilla extract until combined. Set aside.
- In a large bowl, whisk the flour, cocoa powder, baking powder, baking soda, and salt together. Pour the wet ingredients into the dry ingredients and whisk until everything is combined. Fold in the chocolate chips, reserving some for the tops of the warm muffins.
- Spoon the batter evenly into each cup or liner, filling each all the way to the top.
- Bake for 5 minutes at 425°F (218°C); then, keeping the muffins in the oven, reduce heat to 350°F (177°C) and continue baking for another 15–17 minutes or until a toothpick inserted in the center comes out clean. The total time these muffins take in the oven is about 20–21 minutes, give or take. (For mini muffins, bake 11–13 minutes at 350°F (177°C) the whole time.)
- Press any remaining chocolate chips into the tops of the warm muffins. Allow the muffins to cool for 5 minutes in the muffin pan, and then transfer to a wire rack to continue cooling, or enjoy warm.
- Muffins stay fresh covered at room temperature for a few days, then transfer to the refrigerator for up to 1 week.
-
 @ 33baa074:3bb3a297
2025-06-06 02:03:05
@ 33baa074:3bb3a297
2025-06-06 02:03:05Residual chlorinerefers to the residual disinfectant chlorine in tap water. An appropriate amount of residual chlorine can prevent the growth of microorganisms and ensure the safety of water quality. However, when the residual chlorine content in water is too high, it will cause many harms to human health, mainly including the following aspects:
Destruction of nutrients When the residual chlorine content in tap water exceeds the standard, it will destroy the minerals, vitamins and other nutrients, such as vitamin C and vitamin E, when used to wash fruits and vegetables. In the long run, it may cause the human body to absorb these nutrients and lack these essential nutrients.
 Cause chronic poisoning
When tap water containing residual chlorine is used for a long time, the residual chlorine reacts with organic acids and may produce harmful substances such as chloroform and organic lead compounds, which are potential carcinogens. Long-term accumulation may cause chronic poisoning of body organs and pose a threat to human health.
Cause chronic poisoning
When tap water containing residual chlorine is used for a long time, the residual chlorine reacts with organic acids and may produce harmful substances such as chloroform and organic lead compounds, which are potential carcinogens. Long-term accumulation may cause chronic poisoning of body organs and pose a threat to human health.Affect the respiratory system Residual chlorine can cause harm to the human respiratory system, and symptoms such as difficulty breathing and itchy throat may occur. Severe cases may induce rhinitis, bronchitis and even emphysema. In addition, water vapor containing residual chlorine may also cause adverse reactions such as coughing and wheezing after being inhaled.
Damage to the skin Excessive residual chlorine content in water may irritate the skin, easily cause skin dryness, aging, acne and other problems, and may also cause allergic symptoms such as dermatitis and eczema. Prolonged contact with such water may also cause the skin layer to fall off, which is extremely harmful to skin health. Bathing with water containing residual chlorine can also cause hair to become dry, broken, and split.
Other health problems Impact on special groups Pregnant women: Long-term drinking of tap water containing residual chlorine will reduce resistance, affect the growth of the fetal heart and lungs, and may also cause neonatal arrhythmia and lung dysfunction. Children: Long-term drinking of chlorine water will not only hurt the stomach, but also affect nutrient absorption. Moreover, the strong oxidizing hypochlorous acid produced by the reaction of chlorine and water will damage brain cells and affect their development. In addition, chlorine can easily be inhaled into the lungs through the respiratory tract, damaging respiratory cells, and easily leading to asthma and emphysema. Bathing children with water containing residual chlorine will cause their hair to become dry, broken, split, their skin to bleach, their skin to fall off, and they will have allergies. Elderly people: Long-term consumption of chlorinated water is prone to heart disease, coronary atherosclerosis, hypertension and other diseases, and it is also easy to damage the liver and kidneys, increasing the probability of cancer. Gastrointestinal discomfort Long-term drinking of water with excessive residual chlorine content may also cause gastrointestinal discomfort, such as nausea, vomiting, abdominal distension, diarrhea and other symptoms. In severe cases, it may cause gastrointestinal ulcers, bleeding and other diseases.
In order to reduce the harm of residual chlorine in tap water to the human body, it is recommended to avoid directly using tap water containing residual chlorine as much as possible, boil the water before drinking, and use filtering and purification equipment to reduce the residual chlorine concentration in the water if conditions permit, while maintaining a healthy lifestyle and enhancing the body's immunity.
-
 @ da8b7de1:c0164aee
2025-06-05 17:39:41
@ da8b7de1:c0164aee
2025-06-05 17:39:41| Régió/Ország | Fő esemény/politika | Forrás | |------------------|--------------------------------------------------------------------------------------------------|-------------| | Egyesült Államok | Végrehajtási rendeletek a nukleáris termelés négyszeresére növeléséről; a nem létfontosságú K+F költségvetésének csökkentése; SMR és mikroreaktor kezdeményezések | world-nuclear-news, nucnet, aoshearman, ans | | Kanada | Engedélyezés új BWRX-300 SMR reaktor építésére Darlingtonban | world-nuclear-news, ans | | Európa | EU tervek az orosz nukleáris importok korlátozására; Westinghouse–Bulgária beszállítói megállapodások | nucnet, world-nuclear-news | | Globális/Világbank | A nukleáris finanszírozási tilalom esetleges feloldása a fejlődő országok számára | globalissues | | Egyesült Királyság| Új kiberbiztonsági jogszabályok a nukleáris szektorban | aoshearman | | Katonaság/Védelem| A védelmi minisztérium cégeket választott ki mikroreaktorok telepítésére | ans |
Források:
world-nuclear-news
nucnet
aoshearman
globalissues
ans -
 @ 3eba5ef4:751f23ae
2025-06-06 01:59:47
@ 3eba5ef4:751f23ae
2025-06-06 01:59:47加密洞见
解决比特币抗审查交易中继的女巫攻击,社交方案好于技术方案?
Peter Todd 发帖指出,针对比特币抗审查交易中继的攻击行为正在发生——一个名为 garbageman 的节点正在对 Libre Relay 节点采取女巫攻击。这些攻击节点假装支持抗审查交易中继(NODE_LIBRE_RELAY),但实际在暗中丢弃某些交易,目的是阻止特定交易被打包进入区块。作者还介绍了现有防御方法的难度和复杂性,并提出新思路——与其用技术方案解决,不用通过社交解决。他鼓励人们手动与跟他们有个人关系的节点进行连接,原因很简单,人与人的关系可以比任何代码都更有力地评估诚实。
打造统一身份查询标准,提升闪电网络付款体验
比特币开发者 Aviv Bar-el 发表了一项新提案「知名比特币身份端点」(Well-Known Bitcoin Identity Endpoint),旨在通过 HTTPS 标准接口,简化钱包查询用户比特币地址和身份信息的流程,提升链上支付——尤其是闪电网络付款的用户体验和安全性。
通过「承诺/揭示」机制,帮助加强比特币抵御量子计算威胁
Tadge Dryja 提出一种抵御量子计算攻击的比特币软分叉方案。它是「承诺/揭示」(commit / reveal)Fawkescoin 机制的变体,大部分内容与 Tim Ruffing 几年前的方案类似,但也有以下重要区别:
- 该方案不使用加密,而是用更小的基于哈希的承诺,并且描述了如何通过软分叉激活此机制。
- 这个方案仅适用于公钥(或脚本)在链上未公开的输出,例如 pubkey hash 或 script hash 类型;也适用于 Taproot,但必须通过脚本路径花费,因为 Taproot 的 key-path 花费在量子攻击下将不再安全。
- 至于那些公钥已经在链上暴露的输出该如何处理,是另一个独立问题(本方案与「销毁这些币」或「任其被盗」这两种做法都兼容)。
量子危机倒计时:比特币准备好了吗?
Chaincode 在近期发布的报告中,系统分析了「加密相关量子计算」(CRQC,Cryptographically relevant quantum computers)威胁的整体态势,评估了比特币在应对这一转变过程中面临的技术、经济与治理挑战,并表示必须要在早于 CRQC 出现的数年构建起相关共识。重要的结论有:
- 时间窗口:打破比特币椭圆曲线加密基础的 CRQC 可能首先出现在 2030 - 2035 年间。
- 脆弱资金范围:在所有流通的比特币中,约 20-50%(4-1000 万枚 BTC)可能易受 CRQC 攻击。其中远程攻击针对本质上易受攻击的脚本类型(P2PK、P2MS、P2TR)和具有先前暴露的公钥的地址(地址重用),使攻击者能够无限期地从区块链上已有的公共信息中获取私钥;短程攻击会影响所有比特币脚本类型,利用交易广播和确认之间(或之后不久)的漏洞窗口,当公钥暂时暴露时,要求攻击者在几分钟到几小时的时间范围内采取行动。
-
行动战略:建议采用双轨方法,包括:
- 应急措施:在约 2 年内完成对 CRQC 的最低限度但可运作的防护;
- 全面对策:在约 7 年内深入对问题的探索,并开发出功能完备的解决方案
这种双轨策略平衡了眼前的安全需求与最佳抗量子解决方案的严格研究和开发,确保无论 CRQC 能力如何发展,比特币都能做出适当的响应。
利用 zkSNARKs 对比特币交易实施任意约束
对于给比特币交易执行约束,现有的解决方案在隐私或可编程性上都存在不足。本文的研究者利用 zkSNARKs 设计了一种新方案,可以对比特币交易执行任意约束,并保持一定程度的信息私密性。他们方法绕过了比特币脚本的非图灵完备性,允许执行无界约束(unbounded constraints),即重复某个运算的次数次数不受限制。论文全文。
第一个跨比特币和 Cardano 的桥上线
从比特币到 Cardano 的信任最小化 Ordinals 桥通过 Cardinal 协议实现。Cardinal 协议实是一种基于 BitVMX 的信任最小化互作性协议,在不破坏所有权或损害安全性的前提下,它让比特币上中的不可替代资产(如 Ordinals 和 Runes)同 Cardano 链实现了来回移动。
Cardinal 协议背后的技术核心之一是「委员会的验证机制 」(committee-based validation mechanism),遵循 1-out-of-n honest 安全模型。这意味着即使除了一个验证者之外的所有验证者都恶意作,系统仍然保持安全——在增强安全性的同时,还实现了一种更加去中心化和抗审查的方式来在链之间移动资产 。
Thunderbolt 协议:通过 UTXO 捆绑和 OP_CAT 扩展,重构比特币智能合约
Nubit 提出的 Thunderbolt 被认为是为比特币在过去十年中最具里程碑意义的技术升级之一,被视为「Lightning Network 2.0」。Thunderbolt 是一种基于比特币基础层的软分叉升级方法,不依赖二层网络或桥的妥协,而是通过对比特币主链协议层的修改,从根本上增强其可扩展性、交易性能和可编程性。具体而言,Thunderbolt:
- 在吞吐量方面,使用 UTXO 捆绑(UTXO Bundling)技术,实现了对传统比特币交易处理模型的重大优化。
- 在可编程性方面,重新引入并扩展了 OP_CAT 。
- 在资产协议集成方面,Thunderbolt 实施了 Goldinals 统一标准,提供了一个基于零知识证明和状态承诺的资产发行框架。
- 与传统的扩容方法(如侧链、Plasma、Rollup 或桥接包装代币)不同,Thunderbolt 采用原生主链扩容路径。通过 BitVisa 提供去中心化的身份和凭证系统,让交易压缩、智能合约、资产标准集成、链上交易匹配都可以直接在比特币主链上运行。
比特币 2025 大会回顾:政要汇聚、稳定币受关注、DeFi 缺席
今年在拉斯维加斯举行的比特币 2025 大会,汇聚了众多政治要员和企业巨头。美国副总统 JD Vance 对加密货币表明了全力支持,并讨论了比特币在美中竞争中作为战略资产的潜力,他还认为,稳定币不会威胁到美元的完整性,而会使美国的经济实力倍增。白宫加密货币沙皇 David Sacks 发表了会议中最重要的政策公告之一, 暗示根据特朗普建立战略比特币储备的行政命令,美国政府有「获得更多比特币的合法途径」。
此外,关于稳定币立法和加密市场改革受到了很多关注。控制着超过 60% 稳定币市场的 Ardoido 公司表示:「所有传统金融公司都将创建稳定币,提供给他们现有的客户」;而 Tether 表示,其目标市场是全球范围内被排除在银行业之外的人。
这篇总结也提到,与 2022 年和 2023 年的类似峰会不同,今年的大会是由比特币最大化者、Ordinals 创建者、矿业资本家和监管游说者主导,而不再由 DeFi 协议构建者、DAO 运营商或 Layer2 扩容倡导者主导,以太坊和 Solana 生态的开发者缺席。这或许表明:
- 该会议明显的政治基调,使其不适合开发者喜欢的以技术为中心的叙述。
- Web3 建设者和比特币阵营之间的意识形态和叙事分歧可能会越来越大。
精彩无限,不止于链
Sui 攻击事件下的治理再思考:去中心化,程序合法性,和区块链的价值多元性
在受到生态最大的 DEX 项目 Cetus 黑客攻击之后,Sui 网络在协议层面执行了资产冻结和恢复——这是一种有效的技术回应,但同时引发了对抗审查和去中心化等核心区块链原则的批评和辩论。
文章的作者质疑了将去中心化视为唯一至高价值的立场,认为对于大多数有理性者而言,「生活在一个去中心化被认为是最高价值,但当有人侵犯他人财产时,允许强制武力的社会中」都要好于「生活在一个去中心化是唯一至高价值的社会中,因此在任何情况下都不允许强制武力」。
同时作者也指出,Sui 的验证者和网络行为采用的「家长式」治理方式令人失望;此外, Sui 使用委托权益证明(dPoS)系统,其中代币持有者将其代币委托给验证者,验证者代表他们行使相关的投票权,个人因此丧失了投票权。但区块链本来提供了有利于个人的、更加灵活的解决方案,比如 Cosmos 的治理框架就要优于 Sui——对于特定提案,验证人的决定并不会自动代表每个委托人的投票。
在关于去中心化的价值和治理方式之外,文章也提到另一种思考角度——「最重要的是建立与系统愿景相一致的程序合法性」。不同的项目追求不同的目标。就 Sui 而言,其核心目标是使各种资产能够被可靠地定义、并在链上无缝交互。因此,用其他区块链的范式或价值观来理解 Sui 的设计就是不合适的。在特殊情况下,Sui 优先考虑用户资产的返还和生态系统的稳定,而不是严格遵守抗审查——这一决定与其自身的长期愿景更加一致。此外,无论是 Sui 决定不审查相关交易,还是选择对 Cetus 的行为负责,如果背后有程序合法性,这两个决定都是合理的。
基于可信执行环境的私密证明委托
PSE 研究开发团队使用 Intel TDX 构建了一个基于可信执行环境(Trusted Execution Environment)的系统,用于安全的零知识证明委托。该系统允许客户端在不泄露输入的前提下,将大规模的证明任务私密地外包出去。相比受限于硬件能力的移动端本地证明,基于 TEE 的证明方案能够在目前就支持更大规模的陈述,并且随着证明系统的改进持续扩展。作为一种由硬件支撑的解决方案,TEE 能够兼容未来在软件层面的进展(例如更快的证明系统、更高效的工程实现),且只要信任模型被接受,就不会因这些进展而失效。
AI 与 ID:在代理、机器人、深度伪造等世界中的人类证明
我们正处于 AI(包括 AI 智能体、机器人、深度伪造等)深刻改变互联网的时代,随着 AI 的发展,网络上的身份认证变得愈发重要。a16z 的这期播客,讨论了在网上识别人类身份的「人类证明」(proof of human)问题,包括它为何重要,常见的问题有哪些,以及它在底层是如何运作的。
-
 @ 2f5de000:2f9bcef1
2025-06-05 17:33:37
@ 2f5de000:2f9bcef1
2025-06-05 17:33:37I've wanted to write this piece for months. Not because I have anything against Jack Mallers personally - quite the opposite. But because I've watched a pattern emerge in Bitcoin that mirrors one of the most chilling dynamics in Atlas Shrugged: the systematic destruction of our most productive builders by the very people who should be celebrating them.
We are the looters. And Jack might just be our Hank Rearden.
The Underdog's Dilemma
There's a cruel irony in how we treat success in Bitcoin. We champion the underdog, root for the builder in the garage, celebrate the cypherpunk taking on the establishment. But the moment that underdog succeeds - the moment they scale, grow, and inevitably have to navigate the messy realities of the existing system - we turn on them with the ferocity of the same establishment we claim to oppose.\ \ Jack began building Zap (which evolved into Strike) from his parents home in Chicago. Strike has grown into one of the most seamless fiat-to-bitcoin on-ramps for everyday users. No complexity, just pure utility. From day one, he's operated at a level of transparency that would make most CEO's uncomfortable. He's been building in public, taking feedback, admitting mistakes, and iterating - sometimes within hours of criticism.
The Rearden Parallel
In Atlas Shrugged, Hank Rearden creates Rearden Metal - a revolutionary alloy that's stronger, lighter, and more efficient than anything that came before. Instead of celebration, he faces endless scrutiny, regulation, and demands to prove is worthiness. The people who benefit from his innovation spend their time questioning his motives, dissecting his business practices, and demanding he justify his success.
Sound familiar?
Jack comes from a finance background - his father and grandfather were in the industry. This isn't a liability; it's an asset. He understands the beast we're fighting. He's been a Bitcoiner since 2013 with a spotless track record in a space littered with exit scams and broken promises. His values align with proof of work, individualism, and the radical idea that bitcoin is for everyone.
Yet when he helps launch 21 Capital, we don't see innovation - we see betrayal. When he navigates regulatory requirements to build products that can actually reach mainstream adoption, we don't see pragmatism - we see capitulation.
The Scarred Perspective
Our skepticism isn't entirely unfounded. We've been burned before. Mt. Gox, FTX, Three Arrows Capital, Celcius, Terra/ LUNA, BlockFi, Bitconnect, Voyager, QuadrigaCX - the graveyard of Bitcoin is littered with the corpses of trusted institutions. We've learned, painfully, that trust must be earned and verified.
But somewhere along the way, our healthy skepticism has metastasized into destructive paranoia. We've become so focused on protecting ourselves from the next SBF that we're attacking the people building the future we claim to want.
I'm guilty of this myself. I've made scathing attacks on my Nostr feed, comparing Jack to SBF, scrutinising contract clauses about re-hypothecation, and questioning his every move privately. I was viewing his actions through the lens of collective trauma rather than the reality of his long track record.
The Looters Paradox
Here's the uncomfortable truth: we're not just passive observers in this drama. We're active participants. We're the looters.
In Atlas Shrugged, the looters don't necessarily steal directly. They steal time, energy, and focus. They create bureaucracy, demnd endless justification, and burden the productive with the weight of constant explanation. They don't build competing products - they just tear down what others have built.
Everytime we demand Jack explain his business model for the hundredth time, we're stealing his time. Every time we scrutinize his partnerships without offering alternatives, we're creating bureaucracy . Everytime we attack his character rather than his arguments, we're furthering the system we claim to oppose.
The free market will create products whether we like them or not. People will build services that use bitcoin as collateral, create lending products, and navigate regulatory frameworks. The question isn't whether these products will exist - it's whether they'll be built by people who share our values or by those who don't.
The Atlantis Risk
The producers eventually withdraw from society in Atlas Shrugged, retreating to Galt's Gulch (Atlantis) and leaving the looters to face the consequences of their destructive behaviour. The economy collapses because the people who actually build things decided it wasn't worth the hassle anymore.
We're walking dangerously close to this precipice in Bitcoin. We're creating an environment where our most capable builders might just decide it's not worth it. Where the hassle of dealing with our constant scrutiny and bad-faith attacks outweighs the mission of building the future.
Jack has been more patient with our criticism than we deserve. He's addressed concerns publicly, changed the course when necessary, and continued building despite the noise. But patience has limits. At some point, even the most mission-driven builders will ask themselves: "Why am I doing this?"
The Path Forward
I don't know enough about finance to fully understand everything Jack is building with 21 Capital. Neither do most of his critics. But I know enough about Bitcoin to recognise someone who's been fighting the good fight for over a decade.
This doesn't mean we should trust blindly. It doesn't mean we should stop asking questions or demanding transparency. But it does mean we should approach our builders with the same benefit of the doubt we'd want for ourselves.
We need to distinguish between healthy skepticism and destructive paranoia. Between holding people accountable and tearing them down. Between being vigilant and being looters.
The fiat system is the real enemy here. It's massive, entrenched, and infinitely resourcesful. It will adapt, co-opt, and corrupt everything it touches. Fighting it requires builders who are willing to get their hands dirty, navigate imperfect systems, and make pragmatic compromises while holding onto their core values.
We can continue to be looters, tearing down what we don't understand and driving our best builders toward their own version of Atlantis. Or we can be what we claim to be: supporters of the free market, believers of proof of work, and champions of those building the future.
Don't trust. Verify. But remember: verification works both ways.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ 2e8970de:63345c7a
2025-06-05 16:07:04
@ 2e8970de:63345c7a
2025-06-05 16:07:04https://x.com/jburnmurdoch/status/1930203297396249067
https://www.dropbox.com/scl/fi/1lp1dwzx608xdu8jfpkqk/FT_GENDER_DIVIDE_SXSW.pptx?rlkey=9gcwvn77zss3k5l5vgiquennl&e=1&st=apgyr3ug&dl=0
https://stacker.news/items/998014
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 2cde0e02:180a96b9
2025-06-05 15:13:03
@ 2cde0e02:180a96b9
2025-06-05 15:13:03pen & ink; monochromized
Magdalena Carmen Frida Kahlo y Calderón[a] (Spanish pronunciation: [ˈfɾiða ˈkalo]; 6 July 1907 – 13 July 1954[1]) was a Mexican painter known for her many portraits, self-portraits, and works inspired by the nature and artifacts of Mexico. Inspired by the country's popular culture, she employed a naïve folk art style to explore questions of identity, postcolonialism, gender, class, and race in Mexican society.[2] Her paintings often had strong autobiographical elements and mixed realism with fantasy. In addition to belonging to the post-revolutionary Mexicayotl movement, which sought to define a Mexican identity, Kahlo has been described as a surrealist or magical realist.[3] She is also known for painting about her experience of chronic pain.[4]
https://stacker.news/items/997980
-
 @ 975e4ad5:8d4847ce
2025-06-05 13:14:46
@ 975e4ad5:8d4847ce
2025-06-05 13:14:46What is the Fiat System and How Do Central Banks Set Interest Rates?
When central banks expand credit, they often increase the money supply by creating new money through mechanisms like quantitative easing (QE). For instance, a central bank may purchase government bonds, injecting money into the economy. This boosts liquidity but can lead to inflation when too much money chases limited goods and services.
Low interest rates make borrowing cheaper, encouraging spending and investment. However, this can overheat the economy, create speculative bubbles (e.g., in real estate), and drive inflation. Conversely, high interest rates restrict borrowing, slow the economy, and curb inflation but may trigger recessions.
How Would Interest Rates Work Under a Bitcoin Standard?
Under a Bitcoin standard, the money supply is fixed—only 21 million bitcoins will ever exist, with the last one mined around 2140. Unlike the fiat system, no central authority can manipulate the money supply or set interest rates. Instead, interest rates would be determined entirely by the market—by the supply and demand for capital.
If someone wants to borrow bitcoins, the interest rate would depend on negotiations between the lender and borrower. For example, if demand for loans is high and available bitcoins are scarce, interest rates would rise. Conversely, if there are ample bitcoin savings, rates might fall. This process would be fully decentralized and reflect real market conditions, not central bank decisions.
Since new bitcoins cannot be “printed,” there would be no inflation caused by an expanding money supply. Instead, bitcoin’s value would likely rise over time (deflation) as its fixed supply competes with growing demand. This could encourage saving over reckless spending, reshaping economic behavior.
Advantages of a Bitcoin Standard
-
Protection Against Inflation: Bitcoin’s fixed supply prevents currency devaluation, a common issue with fiat money. This safeguards savings and promotes long-term planning.
-
Decentralization: Without a central bank manipulating the market, economic decisions are made by individuals, not bureaucrats. This aligns with free-market principles where competition and innovation thrive.
-
Transparency and Security: The Bitcoin blockchain is public and immutable, ensuring transactions are transparent and secure from tampering.
-
Financial Freedom: Under a Bitcoin standard, individuals have full control over their money without government or bank interference, which is especially crucial in countries with unstable regimes or currencies.
-
Discipline in Lending: Without the ability to print money, lenders would be more cautious, reducing risky investments and speculative bubbles.
Potential Drawbacks and Why a Bitcoin Standard is Superior
One major argument against a Bitcoin standard is that it could slow economic growth. Low interest rates in the fiat system encourage borrowing and spending, driving economic activity. Under a Bitcoin standard, where interest rates are market-driven and likely higher, borrowing would be costlier, potentially limiting investments in new projects.
However, this critique misses a key point: economic growth fueled by artificially low interest rates and money printing is often unsustainable. It leads to debt crises, inflation, and bubbles that eventually burst, as seen in 2008. A Bitcoin standard promotes healthy economic discipline, where investments are based on real value, not artificial capital.
Moreover, bitcoin’s deflationary nature could shift how people view money. Instead of chasing endless growth, societies might prioritize sustainability, innovation, and efficiency. This could lead to a more stable and equitable economy in the long run.
Additional Considerations
A Bitcoin standard could transform global trade. Today, countries with fiat currencies often manipulate exchange rates to gain trade advantages. With bitcoin as a universal currency, such manipulations would vanish, fostering fairer competition.
Another aspect is energy efficiency. While bitcoin mining consumes energy, it incentivizes the development of renewable sources as miners seek cheap, sustainable energy. This could accelerate the transition to a green economy.
Conclusion
The Bitcoin standard offers a vision of an economy rooted in sound money, free markets, and financial freedom. While it may slow certain aspects of economic growth, it creates a more stable and sustainable system that protects individuals from inflation and centralized control. In a world where trust in institutions is waning, the Bitcoin standard is a step toward a fairer and more transparent future.
-
-
 @ 42a071ab:3391e086
2025-06-05 20:06:56
@ 42a071ab:3391e086
2025-06-05 20:06:5688VIN đã từng bước khẳng định vị thế của mình trên thị trường bằng cách không ngừng đầu tư vào chất lượng dịch vụ và sự hài lòng của người dùng. Khác với những nền tảng thông thường, 88VIN chú trọng vào việc xây dựng một hệ sinh thái vận hành bài bản, nơi mọi quy trình đều được chuẩn hóa và tối ưu để đem lại hiệu suất cao nhất. Từ bước đăng ký tài khoản, xác thực thông tin, cho đến nạp – rút tiền và hỗ trợ khách hàng, tất cả đều được thiết kế một cách khoa học, rõ ràng và minh bạch. Sự tiện lợi trong thao tác và tính linh hoạt trong hệ thống đã giúp 88VIN tạo được sự tin tưởng vững chắc từ phía người dùng. Hệ thống hoạt động ổn định, tốc độ xử lý nhanh chóng, cùng đội ngũ chăm sóc khách hàng chuyên nghiệp, nhiệt tình 24/7 chính là những yếu tố làm nên thành công bền vững của 88VIN. Không chỉ vậy, nền tảng còn tích hợp công nghệ bảo mật hiện đại, bảo vệ an toàn tuyệt đối cho mọi thông tin và giao dịch cá nhân, giúp người dùng yên tâm tuyệt đối khi sử dụng.
Bên cạnh sự hoàn hảo về hệ thống, 88VIN còn gây ấn tượng bởi chính sách hỗ trợ người dùng rõ ràng, minh bạch và đầy tính nhân văn. Thay vì chỉ chú trọng vào mặt kỹ thuật, 88VIN hiểu rằng yếu tố con người mới là cốt lõi cho sự phát triển lâu dài. Chính vì vậy, đội ngũ chăm sóc khách hàng tại đây không chỉ được đào tạo bài bản mà còn luôn sẵn sàng lắng nghe, thấu hiểu và đồng hành cùng người dùng trong mọi tình huống. Mỗi phản hồi, dù là nhỏ nhất, đều được ghi nhận nghiêm túc để làm cơ sở nâng cấp chất lượng dịch vụ. Điều này giúp tạo nên một cộng đồng sử dụng 88VIN văn minh, gắn bó và ngày càng phát triển. Đồng thời, việc tối ưu hóa trải nghiệm người dùng được thể hiện qua từng chi tiết nhỏ, từ giao diện hiển thị, bố cục chức năng đến tốc độ phản hồi trên mọi thiết bị. Chính nhờ sự chăm chút tỉ mỉ đó, 88VIN không chỉ đáp ứng nhu cầu trước mắt mà còn luôn sẵn sàng cải tiến để bắt kịp xu hướng trong tương lai.
88VIN không đơn thuần là một nền tảng cung cấp dịch vụ chất lượng cao mà còn là biểu tượng của sự cam kết lâu dài đối với người dùng. Mỗi thành viên khi đến với 88VIN đều được đảm bảo quyền lợi rõ ràng, được đồng hành trong môi trường minh bạch và công bằng. Sự khác biệt của 88VIN chính là khả năng duy trì sự ổn định trong khi vẫn không ngừng đổi mới và hoàn thiện. Những giá trị mà 88VIN theo đuổi không chỉ nằm ở hiệu quả vận hành mà còn là sự tận tâm trong từng trải nghiệm của người dùng. Đây là yếu tố quyết định giúp nền tảng ngày càng chiếm được lòng tin và sự lựa chọn của cộng đồng. Trong thời đại mà sự cạnh tranh ngày càng khốc liệt, việc giữ vững đạo đức kinh doanh, coi trọng người dùng và luôn đặt chất lượng lên hàng đầu chính là con đường bền vững mà 88VIN đang theo đuổi. Nhờ vậy, 88VIN ngày càng khẳng định vị trí vững chắc, trở thành điểm đến tin cậy cho những ai tìm kiếm một nền tảng chuyên nghiệp, ổn định và thực sự vì lợi ích của người dùng.
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ 90c656ff:9383fd4e
2025-06-05 12:27:43
@ 90c656ff:9383fd4e
2025-06-05 12:27:43When people talk about Bitcoin, it’s often described as a digital currency or a “speculative investment.” However, one of Bitcoin’s most fundamental and least understood roles is its function as a settlement network. To understand this, it’s worth comparing it with traditional settlement systems like SWIFT and exploring how Bitcoin offers a foundational layer for global value transfer decentralized and censorship-resistant.
First, let’s explain the difference between liquidity and settlement:
-
Liquidity refers to the ease with which an asset can be converted into “money” without losing value.
-
Settlement is the process of completing a transaction (actual transfer of value between parties).
SWIFT: The communication layer of the traditional financial system
The SWIFT system (Society for Worldwide Interbank Financial Telecommunication) is a network for communication between banks. It doesn’t move money directly but sends standardized messages that instruct financial institutions to perform transfers. The process involves multiple intermediaries, is costly, slow (can take days), and depends on trust between parties and local regulations.
Unlike SWIFT, Bitcoin is a self-sufficient network that enables the direct settlement of value between two parties, without the need for intermediaries. With each block mined, transactions are validated and recorded immutably in a global, transparent, and secure database: the timechain or "blockchain".
01 - Final settlement: Once a transaction is confirmed by a sufficient number of blocks, it is considered final and irreversible.
02 - Censorship resistance: There is no central entity that can block or reverse a valid transaction.
03 - Global availability: The network is accessible 24/7 anywhere in the world with internet access.
Just as gold once served as the foundation of monetary systems, Bitcoin is establishing itself as a base layer of digital value. This layer can support others, such as:
01 - The Lightning Network, which enables near-instant transactions with extremely low fees;
02 - Tokenized financial services, which can use Bitcoin as collateral or for inter-institutional settlement.
By functioning as a public and neutral settlement network, Bitcoin offers an alternative to the traditional system, which is fragmented, closed, and reliant on trust between institutions.
In summary, more than just a speculative asset, Bitcoin is emerging as a global financial infrastructure. As a settlement network, it removes intermediaries, reduces costs, increases security, and democratizes access to value transfer. In an increasingly interconnected and digital world, understanding Bitcoin’s role as a base layer may be key to understanding the future of money.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
-
 @ 502ab02a:a2860397
2025-06-06 01:15:24
@ 502ab02a:a2860397
2025-06-06 01:15:24ปิดท้าย week นี้ด้วยสงครามดีไหมครับ ถ้าอาหารเป็นสนามรบ สิทธิบัตรก็เปรียบเหมือนป้อมปราการ และการฟ้องร้องก็คือปืนใหญ่ยิงสวนกันกลางแดด…ใครที่เคยคิดว่าโลกของอาหารแห่งอนาคตจะสวยงามเพราะเปลี่ยนถั่วเป็นสเต๊ก สกัดกลิ่นเลือดจากพืช หรือหลอกลิ้นให้เชื่อว่า “อร่อยเหมือนเนื้อ” ก็คงต้องมานั่งทบทวนใหม่ว่า โลกใบนี้ไม่ได้ขับเคลื่อนด้วยความฝัน แต่ขับเคลื่อนด้วยเอกสาร 70 หน้าของทนายความ และหมายเรียกจากศาลกลางรัฐเดลาแวร์
Motif FoodWorks เข้ามาในวงการอาหารด้วยวิสัยทัศน์สุดเท่ คือจะสร้างโครงสร้าง-กลิ่น-รส ของโปรตีนอนาคตให้แบรนด์ plant-based ทั่วโลกใช้ได้โดยไม่ต้องเริ่มใหม่ตั้งแต่ศูนย์ เปรียบเหมือนเป็นเบื้องหลังของวงการ มีซอสลับคือ HEMAMI™ ที่สกัดกลิ่นเนื้อจากยีสต์ ผ่านวิธีการทางวิทยาศาสตร์สุดซับซ้อน ฟังแล้วดูดี แต่ปัญหาคือซอสลับของเขาดัน “คล้ายเกินไป” กับของ Impossible Foods ที่ใช้ heme protein เหมือนกัน
แล้วอะไรคือจุดเปราะบางที่ทำให้ Motif ต้องร่วง?
เฮียอยากให้ลองคิดแบบนี้ครับ สมมุติว่ามีร้านกาแฟใหม่ที่ตั้งใจจะขายกาแฟแนวใหม่ ใช้เมล็ดกาแฟหมักยีสต์กลิ่นกล้วยหอม รสชาตินุ่มลึก เป็นของตัวเอง เขาไม่ได้ก็อปสูตรใคร แต่ดันไปใช้กระบวนการคล้ายกับแบรนด์เจ้าตลาดที่เขียนจดสิทธิบัตรเอาไว้ก่อนแล้ว แค่คล้ายก็พอจะโดนลากขึ้นศาลได้ เพราะในโลกของสิทธิบัตร “ความใหม่” และ “ความไม่เหมือน” คือสิ่งศักดิ์สิทธิ์ แม้จะไม่ได้ก็อปตรง ๆ
Impossible Foods เห็นช่องนี้ชัด พวกเขายื่นฟ้องทันที โดยระบุว่า HEMAMI™ ของ Motif ละเมิดสิทธิบัตรเทคนิคการใช้ heme เพื่อสร้างรสชาติเหมือนเนื้อในผลิตภัณฑ์ plant-based ซึ่งเป็นหัวใจหลักที่ Impossible ใช้มัดใจตลาดมาหลายปี
ในเดือนมีนาคม 2022, Impossible Foods ก็ลุกขึ้นมาฟ้อง Motif FoodWorks ต่อศาลรัฐบาลกลางของสหรัฐฯ โดยอ้างว่า HEMAMI™ ละเมิดสิทธิบัตรของตนที่เกี่ยวข้องกับการใช้โปรตีน heme ในการสร้างรสชาติและกลิ่นที่คล้ายเนื้อจริงในผลิตภัณฑ์จากพืช จุดนี้ดูผิวเผินเหมือนแค่ “บริษัท A เหมือนของบริษัท B เลยโดนฟ้อง” แต่ความจริงซับซ้อนและลึกกว่านั้นมาก เพราะทั้งสองบริษัทต่างก็ใช้วิธีผลิตโปรตีน heme ที่คล้ายกันมาก นั่นคือการดัดแปลงพันธุกรรมจุลินทรีย์ให้ผลิตโปรตีนเฉพาะ แล้วหมักออกมาในถังขนาดใหญ่ แต่ต่างกันที่วัตถุดิบและดีไซน์โปรตีน
Impossible Foods ใช้ “soy leghemoglobin” ซึ่งเป็นโปรตีน heme จากรากถั่วเหลือง ส่วน Motif ใช้ “bovine myoglobin” ซึ่งเลียนแบบของวัวจริง ๆ โดยตรง ความคล้ายคือโปรตีนทั้งสองต่างก็ให้กลิ่นคาวแบบเนื้อเมื่อโดนความร้อน และสร้างสีแดงแบบ rare steak ได้เหมือนกัน ทั้งยังถูกหมักด้วยจุลินทรีย์ GMO แบบใกล้เคียงกันอีกด้วย แม้จะต่างสายพันธุ์ของโปรตีน แต่การฟ้องครั้งนี้ตั้งอยู่บนแนวคิดว่า “วิธีการใช้” โปรตีน heme ในอาหารจากพืชอาจเข้าข่ายละเมิดสิทธิบัตร
จากนั้นไม่กี่เดือน Motif ก็สวนกลับโดยการยื่นคำร้อง “Inter Partes Review” (IPR) กับสำนักงานสิทธิบัตรของสหรัฐฯ (USPTO) ผ่าน PTAB ซึ่งเป็นขั้นตอนที่ใช้เพื่อขอให้ตรวจสอบความถูกต้องของสิทธิบัตรที่กำลังมีปัญหา แนวคิดคือถ้าพิสูจน์ได้ว่าสิทธิบัตรของ Impossible นั้นไม่ใหม่จริง หรือมี prior art อยู่ก่อนแล้ว (เช่น งานวิจัยเก่า ๆ ที่ตีพิมพ์ก่อน) ก็จะทำให้สิทธิบัตรนั้นกลายเป็นโมฆะ
Motif ยื่นคำร้องโจมตีสิทธิบัตรถึง 7 ฉบับของ Impossible แบบกระหน่ำชุดใหญ่ ยิงทีเดียวหวังให้สั่นคลอนทั้งระบบ แต่ PTAB รับพิจารณาเพียงฉบับเดียว (หมายเลขสิทธิบัตร 10,933,018) และท้ายที่สุดในเดือนเมษายน 2023 ศาลตัดสินยกเลิกฉบับนั้นจริง โดยให้เหตุผลว่า “ไม่เป็นสิ่งประดิษฐ์ใหม่อย่างเพียงพอ” ซึ่งถือเป็นชัยชนะเล็ก ๆ ของ Motif และสร้างแรงกระเพื่อมในแวดวงวิทยาศาสตร์อาหารอยู่พอสมควร
แต่แม้จะมีชัยบางส่วน อีก 6 ฉบับที่เหลือ PTAB กลับไม่รับพิจารณา โดยบอกว่า “หลักฐานไม่ชัดเจนพอจะเข้าขั้นพิจารณาใหม่” นั่นทำให้ฝั่ง Impossible ยังถือสิทธิบัตรส่วนใหญ่ไว้อยู่เหมือนเดิม แล้วก็เริ่มกลับมาเร่งกระบวนการฟ้องร้องในศาลต่อ ซึ่งหมายความว่า Motif ยิ่งต้องใช้เงินมากขึ้นเรื่อย ๆ ในการสู้รบทั้งสองด้าน ทั้งในศาลและในระบบสิทธิบัตร
ชัยชนะเล็ก ๆ นี้กลายเป็นดาบสองคม เพราะในขณะที่ Motif ดีใจว่าล้มได้ 1 ฉบับ ตลาดกลับมองว่าพวกเขาสู้แบบดิ้นสุดตัว ซึ่งในมุมของนักลงทุน นั่นแปลว่า "ขาดเงินทุนหมุนเวียน" หรือ “มีแนวโน้มขาดทุนต่อเนื่อง” มากกว่าจะมองว่าเป็นฮีโร่สู้เพื่อความถูกต้อง
ระหว่างนี้ Motif ยังพยายาม “spin” ภาพลักษณ์ตัวเองในเชิงบวกอย่างหนัก พวกเขาเปิดตัวผลิตภัณฑ์ใหม่ชื่อ “Motif MoBeef™” และ “Motif MoChicken™” โดยใช้ HEMAMI™ ผสมอยู่ พร้อมโชว์ผลงานให้เชฟชื่อดังระดับ Michelin มาชิมและออกสื่อ โดยหวังว่าจะสร้างความเชื่อมั่นให้ตลาดว่า “ผลิตภัณฑ์เรายังไปต่อได้” และอาจดึงดีลใหม่หรือการลงทุนเพิ่มเข้ามาเพื่อบรรเทาภาระจากการฟ้องร้อง
และในขณะที่ Motif เดินหน้าเปิดตัวผลิตภัณฑ์ใหม่เพื่อแสดงพลังให้ตลาดเห็นว่า “เรายังไปต่อได้” ฝั่ง Impossible กลับเดินเกม PR อย่างเงียบ ๆ ด้วยการแจ้งเตือนสื่อและผู้ถือหุ้นว่า “Motif ยังใช้เทคโนโลยีละเมิดอยู่ต่อเนื่อง” พร้อมแนบเอกสารคำฟ้องเพิ่มในปี 2023 ซึ่งแปลความได้ว่า “ศึกยังไม่จบ อย่าเพิ่งส่งเงินให้คู่แข่งเรา” เพราะในเอกสารคำฟ้องของปี 2023 พวกเขาเสริมข้อกล่าวหาใหม่ว่าการที่ Motif ออกสื่อและใช้ HEMAMI™ ต่อไป “เป็นการจงใจละเมิด” และอาจเข้าข่ายการทำลายคุณค่าของแบรนด์ Impossible โดยตรง จุดนี้ยิ่งทำให้ Motif อยู่ในมุมที่เสี่ยงและลำบากมากขึ้น
การต่อสู้ของทั้งสองบริษัทจึงไม่ใช่แค่เรื่องใครเลียนแบบใคร แต่มันคือเกมยืดเวลา เผาเงิน ปั่นมูลค่า และวัดใจนักลงทุนว่าใครจะถอยก่อนกัน และสุดท้ายคนที่หมดลมหายใจก่อนก็คือ Motif แม้จะมีนักวิทยาศาสตร์เก่ง ๆ เทคโนโลยีล้ำ ๆ หรือวัตถุดิบดีแค่ไหน แต่เมื่อต้องมาสู้กับยักษ์ที่มีสิทธิบัตรในมือ บารมีในตลาด และชื่อเสียงติดหูผู้บริโภค…ก็ยากที่จะเอาชนะด้วยวิทยาศาสตร์เพียงอย่างเดียว
ศึกนี้จึงไม่ได้จบแค่ในศาล แต่มันลากไปถึงห้องประชุมนักลงทุน พาดหัวข่าวใน Business Insider และบอร์ด Reddit ที่คุยกันว่า “Motif จะไปไม่รอดหรือเปล่า” ซึ่งในยุคที่เงินทุนคือออกซิเจน การที่ภาพลักษณ์ของบริษัทเริ่มสั่นคลอน ก็เหมือนถังอากาศรั่วในห้องแล็บใต้ทะเล…ไม่นานนัก Motif ก็เริ่มลดจำนวนพนักงาน ลดเป้าการผลิต และสุดท้าย “ลดบทบาทตัวเองในตลาด”
หากดูเผิน ๆ หลายคนอาจคิดว่านี่คือเรื่องของสองบริษัทใหญ่ในโลก plant-based ที่ทะเลาะกันเอง แต่จริง ๆ แล้วนี่คือบทเรียนใหญ่ของ “วงการอาหารแห่งอนาคต” ที่กำลังเติบโตบนหลังคำว่า IP Intellectual Property ใครถือสิทธิบัตรก่อน คนนั้นตั้งกฎได้ ใครมาใหม่ ถ้าไม่จดให้ไว ก็อาจต้องจ่ายค่าต๋งตลอดชีวิต
และที่เจ็บปวดที่สุดคือบางทีของที่คุณคิดขึ้นมาเอง อาจไม่ใช่ของคุณอีกต่อไปแล้ว ถ้าคุณไม่มีเอกสารในมือ
นี่แหละครับ วงการที่ดูเหมือนจะขาย “นวัตกรรมอาหาร” แต่จริง ๆ แล้วขาย “สิทธิบัตรในกล่องข้าว” ใครจะอยู่ใครจะไป บางทีก็ไม่เกี่ยวกับว่า “ของอร่อยแค่ไหน” แต่เกี่ยวกับว่า “ใครมีทนายเก่งกว่า”
และในขณะที่สองยักษ์ใหญ่ยิงกันด้วยเอกสารละเมิดสิทธิ์ เหยื่อเงียบ ๆ อย่างเกษตรกรรายย่อยที่ยังอยากปลูกผักจริง เลี้ยงวัวจริง หรือแม้แต่ผู้บริโภคที่แค่อยากรู้ว่า “กินอะไรแล้วร่างกายจะดีขึ้น” กลับวนเวียนในทางอยู่ในโลกที่อาหารทุกคำถูกควบคุมโดยทุน จดหมายเรียกจากศาล และวัตถุดิบสังเคราะห์ที่มีรหัสมากกว่าชื่อจริง
สงครามสิทธิบัตรเหล่านี้ไม่เคยมีพื้นที่ให้ชาวไร่ หรือผู้บริโภคธรรมดาเข้าไปมีเสียงเลยสักนิด เพราะมันคือการต่อสู้ระหว่างนักล่าที่ฟาดฟันกันบนยอดห่วงโซ่อาหาร แต่เบื้องล่างของพีระมิด กลับมีแต่เหยื่อที่ถูกเลี้ยงให้งุนงง อยู่กับของปลอม และเชื่อว่า “นี่แหละคืออนาคตของอาหาร”
แล้วใครจะบอกเราว่า...ทางรอดคืออะไร?
คำตอบอาจอยู่ไม่ไกล แค่เราต้องกลับมาถามคำถามง่าย ๆ ที่ใครก็ลืมไปว่า “จริง ๆ แล้ว เราต้องการอาหารแบบไหนกันแน่” อาหารที่กินแล้วแข็งแรง หรืออาหารที่บริษัทแข็งแรง?
เพราะตราบใดที่เรายังปล่อยให้กล่องข้าวอยู่ในมือคนจดสิทธิบัตร เราอาจไม่มีวันได้กลับไปจับจอบเอง ปลูกเอง กินเอง แบบที่มนุษย์เคยเป็นมาก่อนโลกจะกลายเป็นห้องทดลองขนาดยักษ์
ศึกระหว่างผู้ล่ายังรุนแรงขนาดนี้ แล้วศึกระหว่างผู้ล่ากับเหยื่อ จะเหลืออะไรครับ
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 20e7c953:3b8bcb21
2025-06-05 10:46:07
@ 20e7c953:3b8bcb21
2025-06-05 10:46:0721… That number means something. A reminder that limits create value - both in Bitcoin and in life.
Every June 21st, skaters around the world remind us that freedom is something you make yourself - one push at a time only constrained by your own limitations.
This year in Vientiane, we’re proud to support one of the few real skate spots in Laos. A place built and held together by skaters for skaters.
Expect around 50 locals - from young kids to older heads - showing up not just to skate, but to hold space for each other. No ego, no filters, just boards, fun and respect.
Bircoiners have lots to learn from these communities on this regard. Go skate and you'll find out.
SnF
Laostr
Skateboardingisfun
Skate4Fun
Skatestr
-
 @ fd06f542:8d6d54cd
2025-04-15 02:38:14
@ fd06f542:8d6d54cd
2025-04-15 02:38:14排名随机, 列表正在增加中。
Cody Tseng
jumble.social 的作者
https://jumble.social/users/npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wl
- Running [ wss://nostr-relay.app ] (free & WoT) 💜⚡️
- Building 👨💻:
- https://github.com/CodyTseng/jumble
- https://github.com/CodyTseng/nostr-relay-tray
- https://github.com/CodyTseng/danmakustr
- https://github.com/CodyTseng/nostr-relay-nestjs
- https://github.com/CodyTseng/nostr-relay
- https://github.com/CodyTseng
阿甘
- @agan0
- 0xchat.com
- canidae40@coinos.io
- https://jumble.social/users/npub13zyg3zysfylqc6nwfgj2uvce5rtlck2u50vwtjhpn92wzyusprfsdl2rce
joomaen
- Follows you
- joomaen.com
-
95aebd@wallet.yakihonne.com
-
nobot
- https://joomaen.filegear-sg.me/
- https://jumble.social/users/npub1wlpfd84ymdx2rpvnqht7h2lkq5lazvkaejywrvtchlvn3geulfgqp74qq0
颜值精选官
- wasp@ok0.org
- 专注分享 各类 图片与视频,每日为你带来颜值盛宴,心动不止一点点。欢迎关注,一起发现更多美好!
- https://jumble.social/users/npub1d5ygkef6r0l7w29ek9l9c7hulsvdshms2qh74jp5qpfyad4g6h5s4ap6lz
6svjszwk
- 6svjszwk@ok0.org
- 83vEfErLivtS9to39i73ETeaPkCF5ejQFbExoM5Vc2FDLqSE5Ah6NbqN6JaWPQbMeJh2muDiHPEDjboCVFYkHk4dHitivVi
-
low-time-preference
-
anarcho-capitalism
-
libertarianism
-
bitcoin #monero
- https://jumble.social/users/npub1sxgnpqfyd5vjexj4j5tsgfc826ezyz2ywze3w8jchd0rcshw3k6svjszwk
𝘌𝘷𝘦𝘳𝘺𝘥𝘢𝘺 𝘔𝘰𝘳𝘯𝘪𝘯𝘨 𝘚𝘵𝘢𝘳
- everyday@iris.to
- 虽然现在对某些事情下结论还为时尚早,但是从趋势来看,邪恶抬头已经不可避免。
- 我们要做的就是坚持内心的那一份良知,与邪恶战斗到底。
- 黑暗森林时代,当好小透明。
- bc1q7tuckqhkwf4vgc64rsy3rxy5qy6pmdrgxewcww
- https://jumble.social/users/npub1j2pha2chpr0qsmj2f6w783200upa7dvqnnard7vn9l8tv86m7twqszmnke
nostr_cn_dev
npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm@npub.cash
Developed the following products: - NostrBridge, 网桥转发 - TaskQ5, 分布式多任务 - NostrHTTP, nostr to http - Postr, 匿名交友,匿名邮局 - nostrclient (Python client) . -nostrbook, (nostrbook.com) 用nostr在线写书 * https://www.duozhutuan.com nostrhttp demo * https://github.com/duozhutuan/NostrBridge * * https://jumble.social/users/npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm *
CXPLAY
- lightning@cxplay.org
- 😉很高兴遇到你, 你可以叫我 CX 或 CXPLAY, 这个名字没有特殊含义, 无需在意.
- ©本账号下所有内容如未经特殊声明均使用 CC BY-NC-SA 4.0 许可协议授权.
- 🌐如果您在 Fediverse 收到本账号的内容则说明您的实例已与 Mostr.pub 或 Momostr.pink Bridge 互联, 您所看到的账号为镜像, 所有账号内容正在跨网传递. 如有必要请检查原始页面.
- 🧑💻正在提供中文本地化(i10n): #Amethyst #Amber #Citrine #Soapbox #Ditto #Alby
- https://cx.ms/
https://jumble.social/users/npub1gd8e0xfkylc7v8c5a6hkpj4gelwwcy99jt90lqjseqjj2t253s2s6ch58h
w
- 0xchat的作者
- 0xchat@getalby.com
- Building for 0xchat
- https://www.0xchat.com/
- https://jumble.social/users/npub10td4yrp6cl9kmjp9x5yd7r8pm96a5j07lk5mtj2kw39qf8frpt8qm9x2wl
Michael
- highman@blink.sv
- Composer Artist | Musician
- 🎹🎼🎤🏸🏝️🐕❤️
- 在這裡可以看到「我看世界」的樣子
- 他是光良
- https://jumble.social/users/npub1kr5vqlelt8l47s2z0l47z4myqg897m04vrnaqks3emwryca3al7sv83ry3
-
 @ f85b9c2c:d190bcff
2025-06-06 01:02:16
@ f85b9c2c:d190bcff
2025-06-06 01:02:16
Cristiano Ronaldo stands out as a recognized and accomplished football player on a scale. His inspiring journey, from beginnings in Portugal to attaining superstar status serves as an inspiration, to individuals.
Ronaldo’s prodigious talent was evident from a young age. His coach at Sporting CP famously said “He was skinny when he arrived here but with tremendous skill”. Through hard work and dedication, Ronaldo honed his skills
Some Work Ethic and Ambition that Fuelled his success .A key factor in Ronaldo’s success story is his incredible work ethic and winning mentality. He is renowned for his strict training regimen, nutrition plan, and diligent recovery routines. Ronaldo’s dedication to self-improvement paved the way for his success. .Throughout his career, Ronaldo has shown insatiable hunger and ambition to be the best. His drive to succeed and break records is unmatched. Even in the twilight of his career, Ronaldo’s success story continues as he plies his trade in Italy with Juventus.
Lessons from Ronaldo’s Success Story 1. Dedication and hard work are essential Ronaldo showed how training relentlessly can make dreams come true. 2. Believe in your talent Ronaldo had the confidence and work ethic to fulfill his potential. 3. Handle pressure with grace Ronaldo embraced the spotlight and thrived under pressure. 4. Be ambitious and hungry Ronaldo set new benchmarks by constantly raising the bar. 5. Lead by example Ronaldo inspires teammates with his exemplary attitude. 6. Learn and improve Even at the top Ronaldo keeps evolving and adding new skills. 7. Give back Ronaldo uses his global fame and fortune for charity work.
Sum Up Cristiano Ronaldo's remarkable journey showcases the heights that can be reached through a combination of talent and relentless effort. His success serves as an inspiration for anyone with dreams and the determination to make them a reality.
-
 @ 57c631a3:07529a8e
2025-04-07 13:17:50
@ 57c631a3:07529a8e
2025-04-07 13:17:50What is Growth Engineering? Before we start: if you’ve already filled out the What is your tech stack? survey: thank you! If you’ve not done so, your help will be greatly appreciated. It takes 5-15 minutes to complete. Those filling out will receive results before anyone else, and additional analysis from myself and Elin. Fill out this survey here.**
npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m
Growth engineering was barely known a decade ago, but today, most scaleups and many publicly traded tech companies have dedicated growth teams staffed by growth engineers. However, some software engineers are still suspicious of this new area because of its reputation for hacky code with little to no code coverage.
For this reason and others, I thought it would be interesting to learn more from an expert who can tell us all about the practicalities of this controversial domain. So I turned to Alexey Komissarouk, who’s been in growth engineering since 2016, and was in charge of it at online education platform, MasterClass. These days, Alexey lives in Tokyo, Japan, where he advises on growth engineering and teaches the Growth Engineering course at Reforge.
In today’s deep dive, Alexey covers:
- What is Growth Engineering? In the simplest terms: writing code to help a company make more money. But there are details to consider: like the company size where it makes sense to have a dedicated team do this.
- What do Growth Engineers work on? Business-facing work, empowerment and platform work are the main areas.
- Why Growth Engineers move faster than Product Engineers. Product Engineers ship to build: Growth Engineers ship to learn. Growth Engineers do take shortcuts that would make no sense when building for longevity – doing this on purpose.
- Tech stack. Common programming languages, monitoring and oncall, feature flags and experimentation, product analytics, review apps, and more.
- What makes a good Growth Engineer? Curiosity, “build to learn” mindset and a “Jack of all trades” approach.
- Where do Growth Engineers fit in? Usually part of the engineering department, either operating as with an “owner” or a “hitchiker” model.
- Becoming a Growth Engineer. A great area if you want to eventually become a founder or product manager – but even if not, it can accelerate your career growth. Working in Growth forces you to learn more about the business.
With that, it’s over to Alexey:
I’ll never forget the first time I made my employer a million dollars.
I was running a push notification A/B test for meal delivery startup Sprig, trying to boost repeat orders.
A push notification similar to what we tested to boost repeat orders
Initial results were unpromising; the push notification was not receiving many opens. Still, I wanted to be thorough: before concluding the idea was a failure, I wrote a SQL query to compare order volume for subsequent weeks between customers in test vs control.
The SQL used to figure out the push notification’s efficiency
As it turned out, our test group “beat” the control group by around 10%:
‘review_5_push’ was the new type of push notification. Roughly the same amount of users clicked it, but they placed 10% more in orders
I plugged the numbers into a significance calculator, which showed it was statistically significant – or “stat-sig” – and therefore highly unlikely to be a coincidence. This meant we had a winner on our hands! But how meaningful was it, really, and what would adding the push notification mean for revenue, if rolled out to 100% of users?
It turned out this experiment created an additional $1.5 million dollars, annually, with just one push notification. Wow!
I was hooked. Since that day, I've shipped hundreds of experimental “winners” which generated hundreds of millions of incremental revenue for my employers. But you never forget the first one. Moments like this is what growth engineering is all about.
1. What is Growth Engineering?
Essentially, growth engineering is the writing of code to make a company money. Of course, all code produced by a business on some level serves this purpose, but while Product Engineers focus on creating a Product worth paying for, Growth Engineers instead focus on making that good product have a good business. To this end, they focus on optimizing and refining key parts of the customer journey, such as:
- Getting more people to consider the product
- Converting them into paying customers
- Keeping them as customers for longer, and spending more
What kinds of companies employ Growth Engineers? Places you’ve heard of, like Meta, LinkedIn, DoorDash, Coinbase, and Dropbox, are some of the ones I’ve had students from. There’s also OpenAI, Uber, Tiktok, Tinder, Airbnb, Pinterest… the list of high-profile companies goes on. Most newer public consumer companies you’ve heard have a growth engineering org, too.
Typically, growth engineering orgs are started by companies at Series B stage and beyond, so long as they are selling to either consumers or businesses via SaaS. These are often places trying to grow extremely fast, and have enough software engineers that some can focus purely on growth. Before the Series B stage, a team is unlikely to be ready for growth for various reasons; likely that it hasn’t found product-market fit, or has no available headcount, or lacks the visitor traffic required to run A/B tests.
Cost is a consideration. A fully-loaded growth team consisting of a handful of engineers, a PM, and a designer costs approximately 1 million dollars annually. To justify this, a rule of thumb is to have at least $5 million dollars in recurring revenue – a milestone often achieved at around the Series B stage.
Despite the presence of growth engineering at many public consumer tech companies, the field itself is still quite new, as a discipline and as a proper title.
Brief history of growth engineering
When I joined Opendoor in 2016, there was a head of growth but no dedicated growth engineers, but there were by the time I left in 2020. At MasterClass soon after, there was a growth org and a dozen dedicated growth engineers. So when did growth engineering originate?
The story is that its origins lie at Facebook in 2007. The team was created by then-VP of platform and monetization Chamath Palihapitiya. Reforce founder and CEO Brian Balfour shares:
“Growth (the kind found on an org chart) began at Facebook under the direction of Chamath Palihapitiya. In 2007, he joined the early team in a nebulous role that fell somewhere between Product, Marketing, and Operations. According to his retelling of the story on Recode Decode, after struggling to accomplish anything meaningful in his first year on the job, he was on the verge of being fired.Sheryl Sandberg joined soon after him, and in a hail mary move he pitched her the game-changing idea that led to the creation of the first-ever growth team. This idea not only saved his job, but earned him the lion’s share of the credit for Facebook’s unprecedented growth.At the time, Sheryl and Mark asked him, “What do you call this thing where you help change the product, do some SEO and SEM, and algorithmically do this or that?”His response: “I don’t know, I just call that, like, Growth, you know, we’re going to try to grow. I’ll be the head of growing stuff."And just like that, Growth became a thing.”
Rather than focus on a particular product or feature, the growth team at Facebook focused on moving the needle, and figuring out which features to work on. These days, Meta employs hundreds if not thousands of growth engineers.
2. What do Growth Engineers work on?
Before we jump into concrete examples, let’s identify three primary focus areas that a growth engineer’s work usually involves.
- Business-facing work – improving the business directly
- Empowerment work – enabling other teams to improve the business
- Platform work – improving the velocity of the above activities
Let’s go through all three:
Business-facing work
This is the bread and butter of growth engineering, and follows a common pattern:
- Implement an idea. Try something big or small to try and move a key business metric, which differs by team but is typically related to conversion rate or retention.
- Quantify impact. Usually via A/B testing.
- Analyze impact. Await results, analyze impact, ship or roll back – then go back to the first step.
Experiments can lead to sweeping or barely noticeable changes. A famous “I can’t believe they needed to test this” was when Google figured out which shade of blue generates the most clicks. At MasterClass, we tested things across the spectrum:
- Small: should we show the price right on the homepage, was that a winner? Yes, but we framed it in monthly terms of $15/month, not $180/year.
- Medium: when browsing a course page, should we include related courses, or more details about the course itself? Was it a winner? After lengthy experimentation, it was hard to tell: both are valuable and we needed to strike the right balance.
- Large: when a potential customer is interested, do we take them straight to checkout, or encourage them to learn more? Counterintuitively, adding steps boosted conversion!
Empowerment
One of the best ways an engineer can move a target metric is by removing themselves as a bottleneck, so colleagues from marketing can iterate and optimize freely. To this end, growth engineers can either build internal tools or integrate self-serve MarTech (Marketing Technology) vendors.
With the right tool, there’s a lot that marketers can do without engineering’s involvement:
- Build and iterate on landing pages (Unbounce, Instapage, etc)
- Draft and send email, SMS and Push Notifications (Iterable, Braze, Customer.io, etc)
- Connect new advertising partners (Google Tag Manager, Segment, etc)
We go more into detail about benefits and applications in the MarTech section of Tech Stack, below.
Platform work
As a business scales, dedicated platform teams help improve stability and velocity for the teams they support. Within growth, this often includes initiatives like:
- Experiment Platform. Many parts of running an experiment can be standardized, from filtering the audience, to bucketing users properly, to observing statistical methodology. Historically, companies built reusable Experiment Platforms in-house, but more recently, vendors such as Eppo and Statsig have grown in popularity with fancy statistical methodologies like “Controlled Using Pre-Experiment Data” (CUPED) that give more signal with less data.
- Reusable components. Companies with standard front-end components for things like headlines, buttons, and images, dramatically reduce the time required to spin up a new page. No more "did you want 5 or 6 pixels here" with a designer; instead growth engineers rely on tools like Storybook to standardize and share reusable React components.
- Monitoring. Growth engineering benefits greatly from leveraging monitoring to compensate for reduced code coverage. High-quality business metric monitoring tools can detect bugs before they cause damage.
When I worked at MasterClass, having monitoring at the ad layer prevented at least one six-figure incident. One Friday, a marketer accidentally broadened the audience for a particular ad from US-only, to worldwide. In response, the Facebook Ad algorithm went on a spending spree, bringing in plenty of visitors from places like Brazil and India, whom we knew from past experience were unlikely to purchase the product. Fortunately, our monitoring noticed the low-performing campaign within minutes, and an alert was sent to the growth engineer on-call, who immediately reached out to the marketer and confirmed the change was unintentional, and then shut down the campaign.
Without this monitoring, a subtle targeting error like this could have gone unnoticed all weekend and would have eaten up $100,000+ of marketing budget. This episode shows that platform investment can benefit everyone; and since growth needs them most, it’s often the growth platform engineering team which implements them.
As the day-to-day work of a Growth Engineer shows, A/B tests are a critical tool to both measure success and learn. It’s a numbers game: the more A/B tests a team can run in a given quarter, the more of them will end up winners, making the team successful. It’s no wonder, then, that Growth Engineering will pull out all the stops to improve velocity.
3. Why Growth Engineers move faster than Product Engineers
On the surface, growth engineering teams look like product engineering ones; writing code, shipping pull requests, monitoring on-call, etc. So how do they move so much faster? The big reason lies in philosophy and focus, not technology. To quote Elena Verna, head of growth at Dropbox:
“Product Engineering teams ship to build; Growth Engineering teams ship to learn.”
Real-world case: price changes at Masterclass
A few years ago at MasterClass, the growth team wanted to see if changing our pricing model to multiple tiers would improve revenue.
Inspired in part by multiple pricing tiers for competitors such as Netflix (above), Disney Plus, and Hulu.
The “multiple pricing tier” proposal for MasterClass.
From a software engineering perspective, this was a highly complex project because:
- Backend engineering work: the backend did not yet support multiple pricing options, requiring a decent amount of engineering, and rigorous testing to make sure existing customers weren’t affected.
- Client app changes: on the device side, multiple platforms (iOS, iPad, Android, Roku, Apple TV, etc) would each need to be updated, including each relevant app store.
The software engineering team estimated that becoming a “multi-pricing-tier” company would take months across numerous engineering teams, and engineering leadership was unwilling to greenlight that significant investment.
We in growth engineering took this as a challenge. As usual, our goal was not just to add the new pricing model, but to learn how much money it might bring in. The approach we ended up proposing was a Fake Door test, which involves offering a not-yet-available option to customers to gauge interest level. This was risky, as taking a customer who’s ready to pay and telling them to join some kind of waiting list is a colossal waste, and risks making them feel like the target of a “bait and switch” trick.
We found a way. The key insight was that people are only offended about a “bait and switch”, if the “switch” is worse than the “bait.” Telling customers they would pay $100 and then switching to $150 would cause a riot, but starting at $150 and then saying “just kidding, it’s only $100” is a pleasant surprise.
The good kind of surprise.
So long as every test “pricing tier” is less appealing – higher prices, fewer features – than the current offering, we could “upgrade” customers after their initial selection. A customer choosing the cheapest tier gets extra features at no extra cost, while a customer choosing a more expensive tier is offered a discount.
We created three new tiers, at different prices. The new “premium” tier would describe the existing, original offering. Regardless of what potential customers selected, they got this “original offering,” during the experiment.
The best thing about this was that no backend changes were required. There were no real, new, back-end pricing plans; everybody ended up purchasing the same version of MasterClass for the same price, with the same features. The entirety of the engineering work was on building a new pricing page, and the “congratulations, you’ve been upgraded” popup. This took just a few days.
Within a couple of weeks, we had enough data to be confident the financial upside of moving to a multi-pricing-tier model would be significant. With this, we’re able to convince the rest of engineering’s leadership to invest in building the feature properly. In the end, launching multiple pricing tiers turned out to be one of the biggest revenue wins of the year.
Building a skyscraper vs building a tent
The MasterClass example demonstrates the spirit of growth engineering; focusing on building to learn, instead of building to last. Consider building skyscrapers versus tents.
Building a tent optimizes for speed of set-up and tear-down over longevity. You don’t think of a tent as one that is shoddy or low-quality compared to skyscrapers: it’s not even the same category of buildings! Growth engineers maximize use of lightweight materials. To stick with the tents vs skyscraper metaphor: we prioritize lightweight fabric materials over steel and concrete whenever possible. We only resort to traditional building materials when there’s no other choice, or when a direction is confirmed as correct. Quality is important – after all, a tent must keep out rain and mosquitoes. However, the speed-vs-durability tradeoff decision results in very different approaches and outcomes.
4. Tech stack
At first glance, growth and product engineers use the same tooling, and contribute to the same codebases. But growth engineering tends to be high-velocity, experiment-heavy, and with limited test coverage. This means that certain “nice to have” tools for product engineering are mission-critical for growth engineers.
Read more https://connect-test.layer3.press/articles/ea02c1a1-7cfa-42b4-8722-0165abcae8bb
-
 @ e4950c93:1b99eccd
2025-06-05 10:23:39
@ e4950c93:1b99eccd
2025-06-05 10:23:39Marques
Nordkidz est une marque allemande qui crée à la demande des vêtements et linges pour les bébés, les enfants, et un peu pour leurs parents.
Matières naturelles utilisées dans les produits
⚠️ Attention, certains produits de cette marque contiennent des matières non naturelles, dont :
Catégories de produits proposés
Cette marque propose des produits intégralement en matière naturelle dans les catégories suivantes :
Vêtements
- Tailles vêtements : bébés, enfants, unisexe
- Hauts : pulls, t-shirts
- Bas : pantalons, pantalons de survêtement, shorts
- Tête et mains : bonnets, écharpes
Maison
- Linge : housses de pouf, langes, ponchos de bain
Autres informations
👉 En savoir plus sur le site de la marque
Où trouver leurs produits ?
- Nordkidz (en allemand, zone de livraison : Allemagne et Union Européenne) 💚 Via ce lien vous soutenez directement la marque.
📝 Tu peux contribuer à cette fiche en suggérant une modification en commentaire.
🗣️ Tu utilises des produits de cette marque ? Partage ton avis en commentaire.
⚡ Heureu-x-se de trouver cette information ? Soutiens le projet en faisant un don pour remercier les contribut-eur-ice-s.
-
 @ f85b9c2c:d190bcff
2025-06-06 00:24:22
@ f85b9c2c:d190bcff
2025-06-06 00:24:22
Inflation is one of the most significant factors affecting personal wealth and the economy yet it goes unnoticed until its effects become unavoidable. As the cost of goods and services rises, your purchasing power decreases, and this makes long-term financial planning more challenging.
What is inflation? Inflation is the general increase in prices of goods and the reduction of the purchasing power of money. It is commonly measured by : 1.Consumer Price Index (CPI)
2.Core Inflation
3.Producer Price Index (PPI)
Inflation occurs due to various factors, including increased demand and supply chain disruptions
Why is Inflation Important? Inflation is crucial because it affects the cost of living, purchasing power, and the economy as a whole. As prices rise money loses value making it harder for consumers to afford essentials if wages don’t keep up. It also influences interest rates as central banks ,adjust policies to control inflation, borrowing, savings, and investments.
How Inflation Affects Personal Wealth 1. Erosion of Purchasing Power As prices rise, the same amount of money used to buy more before now buys fewer goods and services. 2. Impact on Savings Your money sitting in savings accounts with little or no interest rates loses value over time. If the inflation rate exceeds the interest or profit earned on your savings, then it becomes affected 3. Effects on Investments Their impact is the most because inflation reduces the real value of future payments. 4.Wages & Employment Some businesses may cut costs by reducing roles in a department or reducing pay to keep the team members.
Everyone is affected by inflation.
How Do You Protect Your Wealth from Inflation? 1.Invest in Inflation-Protected Assets Stocks and real estate investments offer long-term growth potential.They give you ownership of a product, which you can use, resell or repackage as you please. 2.Alternative Investments If you have the stomach, commodities, cryptocurrency, and other non-traditional assets may provide inflation releaved. 3. Increase Income Streams Side hustles, passive income, and career advancements can help offset inflation’s impact. 4.Reduce Debt Nigerians are aware of Credit Houses pretending as Loan Sharks chasing debtors around with ridiculous messages of loved ones. In a period of inflation, those loans feel like a double punishment because of ridiculous interest rates and overwhelmed inflation. Whatever you can do to reduce your debt during this period will be life-changing. Also, non-interest debts should always be considered before going down a slippery slope.
Summary Nigeria — A Few Word One thing is clear — inflation persists in almost every corridor of the economy. Inflation is an inevitable part of economic cycles, but understanding its impact allows you to take proactive steps in protecting your wealth. But I believe you can maintain financial stability by following some of the steps above.
Be proactive!
-
 @ fd78c37f:a0ec0833
2025-04-01 11:49:06
@ fd78c37f:a0ec0833
2025-04-01 11:49:06In this edition, we invited Keypleb, the founder of Bitcoin Indonesia, to share how he built the Bitcoin community in Indonesia, overcoming challenges like member turnover and venue selection, while driving the adoption and growth of Bitcoin.
YakiHonne: Welcome, Keypleb. Before we begin, let me briefly introduce YakiHonne. YakiHonne is a decentralized media client built on Nostr—a protocol designed to empower freedom of speech through technology. It enables creators to own their voices and assets while offering innovative tools like smart widgets, verified notes, and support for long-form content. We focus on free speech and free media by user privacy and data to be protected. So before starting the interview, I'd like to hear about yourself and your community.
Keypleb:My name is Keypleb, though it’s a pseudonym—a name I use to respect privacy. I'm a co-founder of Bitcoin Indonesia, Bitcoin House Bali, and Code Orange, a new developer school we launched at a conference just a few days ago. We focus on driving adoption through meetups, hackathons, and technical workshops. I'll dive into more details later, but that's a brief overview. I'm based in Bali now, though I travel a lot and consider myself quite nomadic. Great to be here.
YakiHonne: What sparked your interest in Bitcoin and what motivated you to create a community on Bitcoin?
Keypleb:I first got interested in Bitcoin because it solved a specific problem. At the time, I didn’t know exactly what the solution was, but the problem was that I couldn’t afford a home. Back in 2019, I was living in London, and a two-bedroom apartment was £600,000, which was insanely expensive. First-time buyers like myself simply couldn’t afford it. Why was it so expensive? Why was buying a house so hard? During the COVID lockdown, I had more time on my hands and started listening to Michael Saylor on a Bitcoin podcast, where he talked about how the system is rigged, and that’s why people work hard but still can’t afford a house. That really resonated with me. So I started looking for a community, but unfortunately, there wasn’t one.. Keypleb:After moving to Bali, I attended a lot of crypto meetups, especially scammy altcoin ones, thinking, “There has to be a solution.” But none of them resonated with me. There was no sense of freedom, and no real discussion about inflation resistance. I remembered a podcast from Dea Reskita, an Indonesian host who’s pretty well-known online. I reached out to her and said, “ you’ve got to help me. I’m surrounded by all these shitcoiners, and I can’t take it anymore. I need a real community. Is anything happening?” She replied, “Yes, something is happening. We should restart these meetups next month.” And that’s how it all began. Keypleb:There’s also another story about how we started Bitcoin House and how Bitcoin in Asia came to be, but maybe I’ll save that for later. Anyway, the spark of interest came from Bitcoin solving a real problem, and my drive to keep going came from the lack of quality meetups. Now, we’ve hosted 31 meetups, launched Bitcoin House and Code Orange, and the movement is growing rapidly.

YakiHonne: That’s such an amazing story—going from being on the brink of homelessness to creating something so impactful, and keeping it running every day, bringing new people into the journey. It’s truly inspiring. I’m curious about how the community started. How did you manage to attract members and build a strong community? What challenges did you face along the way?
Keypleb:It all started with our first meetup at the end of 2022, which was two and a half years ago now. At that time, we sent out an email to a group from a previous database, and the first meetup had around 20 people, which was a good start. However, problems quickly arose as people started dropping off, and the community lacked retention. In Bali, people come and go, usually staying for no more than two months, leading to a lack of long-term participation. This became one of our challenges: how to attract more people and, more importantly, get the same people to keep coming back. While I've been coming back for two and a half years, not everyone is able to return as often, and that has been a real challenge. Keypleb:Actually, I should also mention how I met my co-founders—Marius, Diana, and Dimas. We met at the 2023 Indonesia Bitcoin Conference. As time went on, we kept hosting meetups and had a lot of fun each time, though the locations kept changing. One of the initial challenges was that we didn't realize the importance of having a fixed meetup location. We changed venues several times before we realized that having a consistent location is crucial. If anyone wants to run a meetup, it's best to always choose a fixed location. We learned this through trial and error, but now it's no longer an issue. Keypleb:Since the conference, my co-founders and I have been working together, consistently putting in the effort. This is why our community has grown so large—so far, we are hosting 31 monthly meetups, 6 of which are in Bali. This means there is a bitcoin meetup almost every day on a regular basis. We've also established Bitcoin House Bali, a physical space, and the movement is growing rapidly. Without this movement, the region would face many challenges, including inflation and heavy censorship. It all started from just one meetup.
 YakiHonne: It's amazing to see how you met your co-founders and how you’ve built something incredible that continues to grow today. What advice would you give to someone looking to start a successful Bitcoin community right now?
YakiHonne: It's amazing to see how you met your co-founders and how you’ve built something incredible that continues to grow today. What advice would you give to someone looking to start a successful Bitcoin community right now?Keypleb:First, one very important piece of advice is to ensure that every meetup is held at the same location regularly. We realized this challenge through trial and error. To help others who are interested, we’ve published our meetup guide on GitHub, where everyone can check it out. For example, meetups should be held regularly, ideally once a month, or even once a week. In Chiang Mai, the Bitcoin meetup starts every Thursday at 7 PM, and everyone knows the time and location, making it easy to join without having to look up the next meetup. Keypleb:Additionally, our meetup structure is very simple. First, we do a round of introductions where everyone shares their name, where they’re from, and what Bitcoin means to them. This usually takes about 15 minutes. Then, we discuss three main questions: First, why do we need Bitcoin? The discussion typically focuses on two main issues Bitcoin addresses: inflation and censorship;Secondly, how to buy Bitcoin? We usually ask who wants to buy some Bitcoin, and then we do a small purchase together and conduct a P2P trade to demonstrate how easy it is to buy Bitcoin. Lastly, how to store Bitcoin? We introduce self-custody and show how to use hardware wallets (like Trezor), explaining the concept of the 12 words and private keys. Keypleb:The whole meetup usually wraps up in about an hour, after which people can continue socializing at Bitcoin House or wherever the meetup is taking place. In short, keeping the meetup simple and efficient, and ensuring a fixed location for each event, are key factors in building a successful community.
YakiHonne: What's the major approach? Is it more technical, or do you focus on non-technical aspects, or do you cover both?
Keypleb:Our approach includes both technical and non-technical content. Initially, our meetups were completely non-technical, just casual gatherings for people to socialize. Over time, however, we've evolved to incorporate more technical content. Keypleb:Out of the 31 monthly regular meetups we host, most of them have been non-technical, simply regular gatherings held at the same time and place according to our meetup guide. For example, we host the “Bitcoin for Beginners” meetup, which is designed for newcomers and takes place every second Friday of the month at 5 PM at the Bitcoin House Bali. This is entirely non-technical. Additionally, every Wednesday at Bitcoin House, we host the “My First Bitcoin” course. While the course touches on some technical aspects, such as seed phrases and backups, it’s still beginner-friendly and not too technical. The course runs for 10 weeks, and we plan to offer it in the local language at Bali University to help the local community better understand Bitcoin. Keypleb:On the other hand, we also offer highly technical content. We launched a new program called “Code Orange,” which is specifically designed for developers and programmers. We use the “Decoding Bitcoin” website, created by Jamal, which is a learning platform for developers. Many developer schools, like Code Orange, use this resource. Additionally, we host “Code Orange” meetups where we dive into the technical aspects of Bitcoin, such as how mining works and how to prevent single points of failure. Keypleb:We also organize technical workshops, such as “How to Defend Against a Five-Dollar Wrench Attack,” which is closely related to security. Recently, there have been some kidnapping incidents in Bali, and many people are concerned about their Bitcoin being stolen. To address this, we plan to hold a workshop on how to protect Bitcoin against such attacks. Additionally, we host hackathons and other high-tech events, and we just completed a very successful beginner-level hackathon. Keypleb:In summary, our community caters to everyone, from beginners to technical experts. For beginners, we offer easy-to-understand, non-technical content, while for experienced Bitcoiners, we provide in-depth technical material.
 YakiHonne: It's great to approach it in both ways, so everyone gets their own "piece of the cake."Now, I'd like to dive into the technical side. What advice would you give to technically inclined individuals or organizations looking to contribute to the Bitcoin ecosystem? How should they approach the technical aspects of Bitcoin if they want to get involved?
YakiHonne: It's great to approach it in both ways, so everyone gets their own "piece of the cake."Now, I'd like to dive into the technical side. What advice would you give to technically inclined individuals or organizations looking to contribute to the Bitcoin ecosystem? How should they approach the technical aspects of Bitcoin if they want to get involved?Keypleb:I have some additional advice. First, technical individuals can sign up for the “Decoding Bitcoin” course that starts on 18th March 2025 or join our “Code Orange” program and participate in the end-of-year hackathon. If they are technically proficient, this will be a great opportunity. “Decoding Bitcoin” is great for beginners, but it’s also useful for technical individuals. If someone is very skilled, they can start contributing code right away. If they find the course too easy, they can skip it and dive directly into more advanced projects. Additionally, Bitshala and Chaincode Labs offer advanced courses, which more technically advanced individuals can choose to pursue.
 Keypleb:Additionally, it's worth mentioning that the Bitcoin Dev Project has a great platform where technical individuals can find “Good First Issue” or open-source projects to start contributing code. You'll learn about the philosophy behind Bitcoin and why it's more meaningful than other “shitcoins.” Once you’ve taken enough “orange pills” (the philosophy and technology of Bitcoin), you can dive deeper into Bitcoin core development and potentially start coding in C++. If you're interested, you can join specific projects like Nostr, Fedimint or E-Cash.
Keypleb:Additionally, it's worth mentioning that the Bitcoin Dev Project has a great platform where technical individuals can find “Good First Issue” or open-source projects to start contributing code. You'll learn about the philosophy behind Bitcoin and why it's more meaningful than other “shitcoins.” Once you’ve taken enough “orange pills” (the philosophy and technology of Bitcoin), you can dive deeper into Bitcoin core development and potentially start coding in C++. If you're interested, you can join specific projects like Nostr, Fedimint or E-Cash.YakiHonne: I’d like to move on to the next question: How do you see Bitcoin communities evolving as technology progresses, particularly in areas like scalability, privacy, and adaptability to other systems? Keypleb:I believe the Bitcoin community will continue to evolve, and it has already made incredible progress. Two and a half years ago, we started alone in Bali, with just ourselves. We began in the official phase and have had numerous conversations throughout the year. For example, we are now starting a Bitcoin club at a university in Bali; we just need to find a passionate, driven “Bitcoin maximalist,” and the Bitcoin club will begin. Like what our friends did in Banyuwangi, Indonesia, these clubs could eventually evolve into Bitcoin houses.
Keypleb:Regarding privacy and scalability, the community is making strides. We’re big fans of Fedi, which builds on top of the Fedimint protocol and uses e-cash to scale Bitcoin while improving privacy. Fedi low fees and high privacy potential give Bitcoin great opportunities in this area. Keypleb:As for Bitcoin's compatibility with fiat systems, although Bitcoin payments are illegal in some countries like Indonesia, smart developers across Southeast Asia are working on legal solutions. For example, there's a website called Pleb QR that works in Thailand, allowing you to pay in fiat via the Lightning Network. Koral is another app specifically for Indonesia. These kinds of testing products already exist and are physically possible, but we’re just waiting on regulations. My influential friends are actively lobbying the government for adoption. Keypleb:In summary, privacy, scalability, and compatibility with fiat systems are all works in progress, and they will continue to evolve positively. There will be more meetups, more wallet downloads, and more adoption—there’s no doubt about that.
YakiHonne: You mentioned the concept of cross-country issues, so I have one last question: How is the government’s stance on Bitcoin? Is the political climate supportive or against Bitcoin? How do you see the government's approach to Bitcoin in your community or environment?
Keypleb:This reminds me of a person, Jeff Booth, who once said, “We are them, the government is made up of us.” In Indonesia, many politicians actually support Bitcoin, and many of them mine Bitcoin themselves. When money is involved, the incentive is strong, and politicians naturally like to make more money. As a result, Indonesia has a large Bitcoin mining scene. However, overall, the Indonesian government is against Bitcoin, as seen in their ban on Bitcoin payments. The 2011 currency law states that any currency other than the Indonesian Rupiah (IDR) cannot be used, and violators can face up to one year in prison or a fine. This means you cannot pay with US dollars, lira, euros, pesos or pounds. Keypleb:This shows that the government’s legal system is somewhat fragile. It’s understandable that the government is concerned about disruptive technologies like Bitcoin, especially with such a fragile fiat system. Indonesia has also seen many arrests. In 2016, Bank Indonesia issued a letter announcing a crackdown on cryptocurrency payments. Those involved in paying in Bitcoin had their funds seized, and the police cooperated in shutting down businesses accepting Bitcoin payments in the cities. While this isn't very friendly, it does highlight the fragility of the existing system. We also believe that a new executive order may be introduced in the future, similar to when President Roosevelt in 1933 ordered Americans to hand over all their gold with his Executive Order 6102. If it happened before, it could happen again. Keypleb:Therefore, we predict that Bitcoin custody could become a legal issue, which is one of the reasons we blur the faces of participants at every meetup. We need to protect the community from any potential risks. But overall, we remain optimistic. Despite the government ban, the ideology of Bitcoin is unstoppable, and its spread cannot be stopped. So, we are very optimistic about the future.
YakiHonne: I think almost every government around the world, even in Africa, faces similar issues with Bitcoin. Some governments might want Bitcoin but hesitate to openly accept it due to the fear of it undermining the traditional financial system, which, of course, could eventually happen. But hopefully, as the new generation comes into power, we'll see more Bitcoin-friendly governments. So, thank you so much for sharing your insights and advice. I really appreciate your time and the valuable input you've provided.
Keypleb:I'm really glad this conversation enlightened me. I enjoyed it a lot, and it made me reflect on how much work we're doing and how valuable it is. There are a lot of problems out there, with censorship being the biggest one, followed by inflation, which is also a major issue depending on the region. But Bitcoin is open, the community is growing, and people are fighting against censorship and internet shutdowns in places like Indonesia and beyond. The movement is definitely growing. So, I'm very happy to be here and have this chat. Thanks again.
Bitcoin Indonesia nostr: nostr:npub1y4qd2zhtn05gnsaaq5xfejzfk4a32638tx6gpp9g8k6e42g9d66qaxhcr3
Keypleb nostr: nostr:npub190trvg63e6tyqlwlj6lccqpftx76lckj25c006vwx3dzvdl88yxs2nyqdx
-
 @ b1ddb4d7:471244e7
2025-06-05 10:00:43
@ b1ddb4d7:471244e7
2025-06-05 10:00:43Starting January 1, 2026, the United Kingdom will impose some of the world’s most stringent reporting requirements on cryptocurrency firms.
All platforms operating in or serving UK customers-domestic and foreign alike-must collect and disclose extensive personal and transactional data for every user, including individuals, companies, trusts, and charities.
This regulatory drive marks the UK’s formal adoption of the OECD’s Crypto-Asset Reporting Framework (CARF), a global initiative designed to bring crypto oversight in line with traditional banking and to curb tax evasion in the rapidly expanding digital asset sector.
What Will Be Reported?
Crypto firms must gather and submit the following for each transaction:
- User’s full legal name, home address, and taxpayer identification number
- Detailed data on every trade or transfer: type of cryptocurrency, amount, and nature of the transaction
- Identifying information for corporate, trust, and charitable clients
The obligation extends to all digital asset activities, including crypto-to-crypto and crypto-to-fiat trades, and applies to both UK residents and non-residents using UK-based platforms. The first annual reports covering 2026 activity are due by May 31, 2027.
Enforcement and Penalties
Non-compliance will carry stiff financial penalties, with fines of up to £300 per user account for inaccurate or missing data-a potentially enormous liability for large exchanges. The UK government has urged crypto firms to begin collecting this information immediately to ensure operational readiness.
Regulatory Context and Market Impact
This move is part of a broader UK strategy to position itself as a global fintech hub while clamping down on fraud and illicit finance. UK Chancellor Rachel Reeves has championed these measures, stating, “Britain is open for business – but closed to fraud, abuse, and instability”. The regulatory expansion comes amid a surge in crypto adoption: the UK’s Financial Conduct Authority reported that 12% of UK adults owned crypto in 2024, up from just 4% in 2021.
Enormous Risks for Consumers: Lessons from the Coinbase Data Breach
While the new framework aims to enhance transparency and protect consumers, it also dramatically increases the volume of sensitive personal data held by crypto firms-raising the stakes for cybersecurity.
The risks are underscored by the recent high-profile breach at Coinbase, one of the world’s largest exchanges.
In May 2025, Coinbase disclosed that cybercriminals, aided by bribed offshore contractors, accessed and exfiltrated customer data including names, addresses, government IDs, and partial bank details.
The attackers then used this information for sophisticated phishing campaigns, successfully deceiving some customers into surrendering account credentials and funds.
“While private encryption keys remained secure, sufficient customer information was exposed to enable sophisticated phishing attacks by criminals posing as Coinbase personnel.”
Coinbase now faces up to $400 million in compensation costs and has pledged to reimburse affected users, but the incident highlights the systemic vulnerability created when large troves of personal data are centralized-even if passwords and private keys are not directly compromised. The breach also triggered a notable drop in Coinbase’s share price and prompted a $20 million bounty for information leading to the attackers’ capture.
The Bottom Line
The UK’s forthcoming crypto reporting regime represents a landmark in financial regulation, promising greater transparency and tax compliance. However, as the Coinbase episode demonstrates, the aggregation of sensitive user data at scale poses a significant cybersecurity risk.
As regulators push for more oversight, the challenge will be ensuring that consumer protection does not become a double-edged sword-exposing users to new threats even as it seeks to shield them from old ones.
-
 @ fbf0e434:e1be6a39
2025-06-05 14:08:24
@ fbf0e434:e1be6a39
2025-06-05 14:08:24Hackathon 概要
ETHBratislava Hackathon Vol.2 汇聚 54 名开发者并审核通过 11 个项目,成为以太坊社区的重要盛事。此次黑客马拉松在斯洛伐克技术大学举办,参与者可免费参与 ETHBratislava 大会,这一安排助力开发者探索区块链技术的前沿进展。
项目在解决以太坊可扩展性与互操作性问题上成果显著,尤其在 “World Computer” 赛道表现突出。“Zircuit Restaking Track” 赛道也带来重要创新,聚焦通过 AI 驱动的 zk rollups 技术提升安全性与扩展性。“European Stablecoin EURØP Challenge” 则致力于开发欧元背书的稳定币,推动欧洲监管数字货币概念落地。
参与者不仅获得资深导师指导、与行业领袖建立连接的机会,现场更有招聘方挖掘技术人才。活动在兼具庆祝与社交属性的派对中落幕。总计 4,000 欧元奖金的设置,营造了开发者之间竞争与合作并存的创新氛围。ETHBratislava Vol.2 成功孵化出影响以太坊未来的创新构想,同时强化了社区联结。
Hackathon 获奖者
World Computer 奖项获奖者
此类别着重于利用以太坊能力的面向消费者的应用程序。开发者创建了解决方案,旨在增强包容性、金融工具和教育平台。获奖者包括:
- Zhar: 该去中心化平台使用AI和以太坊区块链来管理、执行和激励使用智能合约和代币的链上挑战。
- Ledger Lens: 一个Web应用程序,促进对以太坊多层生态系统的可视化和分析,强调代币流动和跨链桥使用等指标。
现实世界代币化奖项获奖者
此类别集中于在欧洲利用EUR锚定的稳定币EURØP构建效用。项目目标是在此数字货币之上部署初步技术增强。
- dEST: 一个去中心化平台,利用NFTs和智能合约来促进无中介的代币化房地产交易。
- EnergyHub: 一个提供去中心化平台以货币化多余绿色能源并通过智能合约和用户友好的仪表板实现能源捐赠的应用程序。
Restaking 奖项获奖者
此类别鼓励团队在Zircuit生态系统内的AI驱动zkEVM上进行构建,着重于支持AI增强安全性和创新zk rollup技术的项目。
- RestakerX: 一个仪表板应用程序,设计用于跟踪Zircuit网络上的数字资产,提供算法建议以最大化收益。
有关所有项目的更多详细信息和此次黑客马拉松中展示的创新理念的进一步见解,请访问 ETHBratislava Hackathon页面。
关于组织者
Ethereum Bratislava
Ethereum Bratislava 是中欧和东欧地区区块链和技术领域的一个重要社区,致力于推进以太坊的开发和整合。由一支专家团队支持,该组织在增强以太坊在中欧和东欧地区的可扩展性和安全性的项目中作出了重大贡献。积极参与社区活动和教育活动强调了他们在区块链领域促进技术创新和知识共享的承诺。Ethereum Bratislava 继续支持技术改进和生态系统增长,旨在增强以太坊的能力和跨各行业的采用。
-
 @ 1c5ff3ca:efe9c0f6
2025-06-05 06:29:45
@ 1c5ff3ca:efe9c0f6
2025-06-05 06:29:45Just calling it Open is not enough - Herausforderungen öffentlicher Bildungsinfrastrukturen und wie Nostr helfen könnte
Ich möchte gerne mit euch teilen, an welchen Konzepten ich arbeite, um die öffentliche Bildungsinfrastruktur mit Hilfe von Nostr zugänglicher und offener zu gestalten. Ich arbeite im Bereich öffentlicher Bildungsinfrastrukturen, besonders im Feld von Open Educational Resources (#OER). OER sind offen lizenzierte Bildungsmaterialien, die mit einer offenen Lizenz, meist einer Creative Commons Lizenz, versehen sind (CC-0, CC-BY, CC-BY-SA). Durch die klare und offene Lizenzierung ist es leicht möglich, die Lernmaterialien auf die individuellen Bedarfe anzupassen, sie zu verbessern und sie erneut zu veröffentlichen.
Seit vielen Jahren wird einerseits die Entwicklung freier Bildungsmaterialien gefördert, andererseits werden Plattformen, insbesondere Repositorien gefördert, die diese Materialien verfügbar machen sollen. Denn irgendwo müssen diese Materialien zur Verfügung gestellt werden, damit sie auch gefunden werden können.
Das klappt allerdings nur so mittelgut.
Herausforderungen
Nach vielen Jahren Förderung kann die einfache Frage: "Wo kann ich denn mein OER-Material bereitstellen" nicht einfach beantwortet werden. Es gibt Services, bei denen ich mein OER hochladen kann, jedoch bleibt es dann eingeschlossen in dieser Plattform und wird nicht auf anderen Plattformen auffindbar. Außerdem sind diese Services häufig an bestimmte Bildungskontexte gebunden oder geben Content erst nach einer Qualitätsprüfung frei. Dies führt dazu, dass ein einfaches und gleichzeitig öffentliches Teilen nicht möglich ist.
Diese und weitere Herausforderungen haben ihren Ursprung darin, dass Service und Infrastruktur in der Architektur öffentlichen Bildungsarchitektur ungünstig vermischt werden. Als Infrastruktur verstehe ich hier die Bereitstellung einer öffentlichen und offen zugänglichen Bildungsinfrastruktur, auf der Daten ausgetauscht, also bereitgestellt und konsumiert werden können. Jedoch existiert eine solche Infrstruktur momentan nicht unabhängig von den Services, die auf ihr betrieben werden. Infrastrukturbetreiber sind momentan gleichzeitig immer Servicebetreiber. Da sie aber die Hand darüber haben wollen, was genau in ihrem Service passiert (verständlich), schränken sie den Zugang zu ihrer Infrastruktur mit ein, was dazu führt, dass sie Lock-In Mechanismen großer Medienplattformen in der kleinen öffentlichen Bildungsinfrastruktur replizieren.
Es ist in etwas so, als würde jeder Autobauer auch gleichzeitig die Straßen für seine Fahrzeuge bauen. Aber halt nur für seine Autos.
Anhand einiger beispielhafter Services, die bestehende Plattformen auf ihren Infrastrukturen anbieten, möchte ich die Herausforderungen aufzeigen, die ich im aktuellen Architekturkonzept sehe:
- Upload von Bildungsmaterial
- Kuration: Zusammenstellung von Listen, Annotation mit Metadaten
- Crawling, Indexierung und Suche
- Plattfformübergreifende Kollaboration in Communities -> Beispiel: Qualitätssicherung (was auch immer das genau bedeutet)
- KI- Services -> Beispiel: KI generierte Metadaten für BiIdungsmaterial
Material Upload
Der Service "Material-Upload" oder das Mitteilen eines Links zu einem Bildungsmaterial wird von verschiedenen OER-Pattformen bereitgestellt (wirlernenonline.de, oersi.org, mundo.schule).
Dies bedeutet konkret: Wenn ich bei einer der Plattformen Content hochlade, verbleibt der Content in der Regel auch dort und wird nicht mit den anderen Plattformen geteilt. Das Resultat für die User: Entweder muss ich mich überall anmelden und dort mein Material hochladen (führt zu Duplikaten) oder damit leben, dass eben nur die Nutzer:innen der jeweiligen Plattform meinen Content finden können.
Der "Open Educational Resource Search Index" (OERSI) geht diese Herausforderung an, indem die Metadaten zu den Bildungsmaterialien verschiedener Plattformen in einem Index bereitgestellt werden. Dieser Index ist wiederum öffentlich zugänglich, sodass Plattformen darüber auch Metadaten anderer Plattformen konsumieren können. Das ist schon sehr gut. Jedoch funktioniert das nur für Plattformen, die der OERSI indexiert und für alle anderen nicht. Der OERSI ist auf den Hochschulbereich fokussiert, d.h. andere Bildungskontexte werden hier ausgeschlossen. Der Ansatz für jeden Bildungsbereich einen passenden "OERSI" daneben zustellen skaliert und schlecht und es bleibt die Herausforderung bestehen, dass für jede Quelle, die indexiert werden soll, ein entsprechender Importer/Crawler geschrieben werden muss.
Dieser Ansatz (Pull-Ansatz) rennt den Materialien hinterher.
Es gibt jedoch noch mehr Einschränkungen: Die Plattformen haben sich jeweils auf spezifische Bildungskontexte spezialisiert. D.h. auf die Fragen: Wo kann ich denn mein OER bereitstellen, muss immer erst die Gegenfrage: "Für welchen Bildungsbereich denn?" beantwortet werden. Wenn dieser außerhalb des allgemeinbildendenden Bereichs oder außerhalb der Hochschule liegt, geschweige denn außerhalb des institutionellen Bildungsrahmens, wird es schon sehr, sehr dünn. Kurzum:
- Es ist nicht einfach möglich OER bereitzustellen, sodass es auch auf verschiedenen Plattformen gefunden werden kann.
Kuration
Unter Kuration verstehe ich hier die Zusammenstellung von Content in Listen oder Sammlungs ähnlicher Form sowie die Annotation dieser Sammlungen oder des Contents mit Metadaten.
Einige Plattformen bieten die Möglichkeit an, Content in Listen einzuordnen. Diese Listen sind jedoch nicht portabel. Die Liste, die ich auf Plattform A erstelle, lässt sich nicht auf Plattform B importieren. Das wäre aber schön, denn so könnten die Listen leichter auf anderen Plattformen erweitert oder sogar kollaborativ gestaltet werden, andererseits werden Lock-In-Effekte zu vermieden.
Bei der Annotation mit Metadaten treten verschiedene zentralisierende Faktoren auf. In der momentanen Praxis werden die Metadaten meist zum Zeitpunkt der Contentbereitstellung festgelegt. Meist durch eine Person oder Redaktion, bisweilen mit Unterstützung von KI-Services, die bei der Metadateneingabe unterstützen. Wie aber zusätzliche eigene Metadaten ergänzen? Wie mitteilen, dass dieses Material nicht nur für Biologie, sondern auch für Sport in Thema XY super einsetzbar wäre? Die momentanen Ansätze können diese Anforderung nicht erfüllen. Sie nutzen die Kompetenz und das Potential ihrer User nicht.
- Es gibt keine interoperablen Sammlungen
- Metadaten-Annotation ist zentralisiert
- User können keine eigenen Metadaten hinzufügen
Crawling, Indexierung und Suche

Da die Nutzer:innen nicht viele verschiedene Plattformen und Webseiten besuchen wollen, um dort nach passendem Content zu suchen, crawlen die "großen" OER-Aggregatoren diese, um die Metadaten des Contents zu indexieren. Über verschiedene Schnittstellen oder gerne auch mal über das rohe HTML. Letztere Crawler sind sehr aufwändig zu schreiben, fehleranfällig und gehen bei Design-Anpassungen der Webseite schnell kaputt, erstere sind etwas stabiler, solange sich die Schnittstelle nicht ändert. Durch den Einsatz des Allgemeinen Metadatenprofils für Bildungsressourcen (AMB) hat sich die Situation etwas verbessert. Einige Plattformen bieten jetzt eine Sitemap an, die Links zu Bildungsmaterial enthalten, die wiederum eingebettet
script-tags vom Typapplication/ld+jsonenthalten, sodass die Metadaten von dort importiert werden können.Beispiel: e-teaching.org bietet hier eine Sitemap für ihre OER an: https://e-teaching.org/oer-sitemap.xml und auf den jeweiligen Seiten findet sich ein entsprechendes script-Tag.
Das ist schon viel besser, aber da geht noch mehr:
Zunächst ist dieser Ansatz nur für Plattformen und Akteure praktikabel, die über IT-Ressourcen verfügen, um entsprechende Funktionalitäten bei sich einbauen zu können. Lehrende können dies nicht einfach auf ihrem privaten Blog oder ähnliches umsetzen. Zum anderen besteht immer noch ein Discovery Problem. Ich muss nach wie vor wissen, wo ich suchen muss. Ich muss die Sitemaps kennen, sonst finde ich nichts. Statt eines Ansatzes, bei dem Akteure eigenständig mitteilen können, dass sie neuen Content haben (Push-Ansatz), verfolgen wir derzeit einen Ansatz, bei dem jede Plattform für sich Content im Pull-Verfahren akquiriert. Dies führt an vielen Stellen zu Doppelarbeiten, ist ineffizient (mehrere Personen bauen genau die gleichen Crawler, aber halt immer für ihre Plattform) und schliesst vor allem kleine Akteure aus (lohnt es sich einen Crawler zu programmieren, wenn die Webseite "nur" 50 Materialien bereitstellt?).
Anstatt erschlossene Daten zu teilen, arbeiten die Plattformen für sich oder stellen es höchstens wieder hinter eigenen (offenen oder geschlossenen) Schnittstellen bereit. Das ist wohl nicht das, was wir uns unter einer offenen und kollaborativen Gemeinschaft vorstellen, oder?
Bei der Suche stehen wir vor ähnlichen Herausforderungen, wie bereits oben geschildert. Obwohl verschiedene OER-Aggregatoren in Form von Repositorien oder Referatorien bereits viele der "kleineren" Plattformen indexieren und somit eine übergreifende Suche anbieten, ist es nicht möglich, diese Aggregatoren gemeinsam zu durchsuchen. Dies führt im Endeffekt dazu, dass die User wieder verschiedene Plattformen ansteuern müssen, wenn sie den gesamten OER-Fundus durchsuchen wollen.
- An vielen Stellen wird Content doppelt erschlossen, aber immer für die eigene Plattform
- Es gibt keinen geteilten Datenraum, in den Akteure Content "pushen" können
- Es gibt keine plattformübergreifenden Suchmöglichkeiten
Plattformübergreifende Kollaboration
Das wäre schön, oder? Mir ist schleierhaft, wie #OEP (Open Educational Practices, genaue Definition durch die Community steht noch aus) ohne funktionieren soll. Aber es gibt meines Wissens nach nicht mal Ansätze, wie das technisch umgesetzt werden soll (oder doch? let me hear).
Ein Szenario für solche plattformübergreifende Kollaboration könnte Qualitätssicherung sein. Gesetzt, dass sich zwei Plattformen / Communities auf etwas verständigt haben, dass sie als "Qualität" bezeichnen, wie aber dieses Gütesiegel nun an den Content bringen?
Plattform A: Na, dann kommt doch alle zu uns. Hier können wir das machen und dann hängt auch ein schönes Badge an den Materialien.
Plattform B: Ja, aber dann hängt es ja nicht an unseren Materialien. Außerdem wollen/müssen wir bei uns arbeiten, weil welche Existenzberechtigung hat denn meine Plattform noch, wenn wir alles bei dir machen?
- Obwohl nun #OEP in aller Munde sind, gibt es keine technischen Ansätze, wie (plattformübergreifende) Kollaboration technisch abgebildet werden kann
KI-Services
Was ist heute schon komplett ohne das Thema KI zu erwähnen? Mindestens für den nächsten Förderantrag muss auch irgendetwas mit KI gemacht werden...
Verschiedene Projekte erarbeiten hilfreiche und beeindruckende KI-Services. Beispielsweise, um die Annotation von Content mit Metadaten zu erleichtern, Metadaten automatisch hinzuzufügen, Content zu bestimmten Themen zu finden oder (halb-)automatisch zu Sammlungen hinzuzufügen. Aber (vielleicht habt ihr es schon erraten): Funktioniert halt nur auf der eigenen Plattform. Vermutlich, weil die Services nah am plattformeigenen Datenmodell entwickelt werden. Und da die Daten dieses Silo nicht verlassen, passt das schon. Das führt dazu, dass an mehreren Stellen die gleichen Services doppelt entwickelt werden.
- KI-Services funktionieren oft nur auf der Plattform für die sie entwickelt werden
Zusammenfassung der Probleme
Wir machen übrigens vieles schon sehr gut (Einsatz des AMB, Offene Bidungsmaterialien, wir haben eine großartige Community) und jetzt müssen wir halt weiter gehen.
(Die OER-Metadatengruppe, die das Allgemeine Metadatenprofil für Bildungsressourcen (AMB) entwickelt hat, bekommt für ihre Arbeit keine direkte Förderung. Gleichzeitig ist sie eine zentrale Anlaufstelle für alle, die mit Metadaten in offenen Bildungsinfrastukturen hantieren und das Metadatenprofil ist eines der wenigen Applikationsprofile, das öffentlich einsehbar, gut dokumentiert ist und Validierungsmöglichkeiten bietet.)
Betrachten wir die gesamten Plattformen und die beschriebenen Herausforderungen aus der Vogelperspektive, so lassen sich drei ineinander verschränkte Kernbestandteile unterscheiden, die helfen, die beschriebenen Probleme besser zu verstehen:
- User
- Service
- Daten
User: Auf (fast) allen Plattformen agieren User. Sie laden Material hoch, annotieren mit Metadaten, sind in einer Community, suchen Content usw. Egal, ob sie sich einloggen können/müssen, irgendetwas bieten wir unseren Usern an, damit sie daraus hoffentlich Mehrwerte ziehen
Service: Das ist dieses irgendetwas. Die "Webseite", die Oberfläche, das, wo der User klicken und etwas tun kann. Es ist das, was den Daten oft eine "visuelle" Form gibt. Der Service ist der Mittler, das Interface zwischen User und Daten. Mithilfe des Services lassen sich Daten erzeugen, verändern oder entfernen (Es gibt natürlich auch viele nicht-visuelle Services, die Interaktion mit Daten ermöglichen, aber für die meisten normalen Menschen, gibt es irgendwo was zu klicken).
Daten: Die Informationen in strukturierter maschinenlesbarer Form, die dem User in gerenderter Form durch einen Service Mehrwerte bieten können. Ungerenderte Daten können wir schwieirg erfassen (wir sind ja nicht Neo). Das können entweder die Metadaten zu Bildungmaterialien sein, die Materialien selbst, Profilinformationen, Materialsammlungen o.ä.

Meines Erachtens nach haben viele der oben beschriebenen Herausforderungen ihren Ursprung darin, dass die drei Kernbestandteile User, Service, Daten ungünstig miteinander verbunden wurden. Was kein Vorwurf sein soll, denn das ist genau die Art und Weise, wie die letzten Jahre (Jahrzehnte?) Plattformen immer gebaut wurden:
- User, Service und Daten werden in einer Plattform gebündelt
Das heisst durch meinen Service agieren die User mit den Daten und ich kann sicherstellen, dass in meiner kleinen Welt alles gut miteinander funktioniert. Sinnvoll, wenn ich Microsoft, Facebook, X oder ähnliches bin, weil mein Geschäftsmodell genau darin liegt: User einschließen (lock-in), ihnen die Hohheit über ihren Content nehmen (oder kannst du deine Facebook Posts zu X migrieren?) und nach Möglichkeit nicht wieder rauslassen.
Aber unsere Projekte sind öffentlich. Das sind nicht die Mechanismen, die wir replizieren sollten. Also was nun?
Bildungsinfrasstrukturen auf Basis des Nostr-Protokolls
Nostr
Eine pseudonyme Person mit dem Namen "fiatjaf" hat 2019 ein Konzept für ein Social Media Protokoll "Nostr - Notes and Other Stuff Transmitted By Relays" wie folgt beschrieben:
It does not rely on any trusted central server, hence it is resilient, it is based on cryptographic keys and signatures, so it is tamperproof, it does not rely on P2P techniques, therefore it works.
Fiatjaf, 2019
Die Kernbestandsteile des Protokolls bestehen aus:
- JSON -> Datenformat
- SHA256 & Schnorr -> Kryptographie
- Websocket -> Datenaustausch
Und funktionieren tut es so:
User besitzen ein "Schlüsselpaar": einen privaten Schlüssel (den behälst du für dich, nur für dich) und einen öffentlichen Schlüssel, den kannst du herumzeigen, das ist deine öffentliche Identität. Damit sagst du anderen Usern: Hier schau mal, das bin ich. Die beiden Schlüssel hängen dabei auf eine "magische" (kryptografische) Weise zusammen: Der öffentliche Schlüssel lässt sich aus dem privaten Schlüssel generieren, jedoch nicht andersherum. D.h. falls du deinen öffentlichen Schlüssel verlierst: Kein Problem, der lässt sich immer wieder herstellen. Wenn du deinen privaten Schlüssel verlierst: Pech gehabt, es ist faktisch unmöglich, diesen wieder herzustellen.
Die Schlüsselmagie geht jedoch noch weiter: Du kannst mit deinem privaten Schlüssel "Nachrichten" signieren, also wie unterschreiben. Diese Unterschrift, die du mit Hilfe des privaten Schlüssels erstellst, hat eine magische Eigenschaft: Jeder kann mithilfe der Signatur und deinem öffentlichen* Schlüssel nachprüfen, dass nur die Person, die auch den privaten Schlüssel zu diesem öffentlichen Schlüssel besitzt, diese Nachricht unterschrieben haben kann. Magisch, richtig? Verstehst du nicht komplett? Nicht schlimm, du benutzt es bereits vermutlich, ohne dass du es merkst. Das ist keine fancy neue Technologie, sondern gut abgehangen und breit im Einsatz.
Merke: User besitzen ein Schlüsselpaar und können damit Nachrichten signieren.
Dann gibt es noch die Services. Services funktionieren im Grunde wie bereits oben beschrieben. Durch sie interagieren die User mit Daten. Aber bei Nostr ist es ein kleines bisschen anders als sonst, denn: Die Daten "leben" nicht in den Services. Aber wo dann?
Wenn ein User einen Datensatz erstellt, verändert oder entfernen möchte, wird dieses "Event" (so nennen wir das bei Nostr) mit deinem privaten Schlüssel signiert (damit ist für alle klar, nur du kannst das gemacht haben) und dann mehrere "Relays" gesendet. Das sind die Orte, wo die Daten gehalten werden. Wenn ein User sich in einen Service einloggt, dann holt sich der Service die Daten, die er braucht von diesen Relays. User, Service und Daten sind also entkoppelt. Der User könnte zu einem anderen Service wechseln und sich dieseleben Daten von den Relays holen. Keine Lock-In Möglichkeiten.
Merke: User, Service und Daten sind entkoppelt.
Zuletzt gibt es noch die Relays. Relays sind Orte. Es sind die Orte, zu denen die Events, also die Daten der User, ihre Interaktionen, gesendet und von denen sie angefragt werden. Sie sind sowas wie das Backend von Nostr, allerdings tun sie nicht viel mehr als das: Events annehmen, Events verteilen. Je nach Konfiguration dürfen nur bestimmte User auf ein Relay schreiben oder davon lesen.
Das Protokoll ist von seinem Grunddesign auf Offenheit und Interoperabilität ausgelegt. Keine Registrierung ist nötig, sondern nur Schlüsselpaare. Durch kryptografische Verfahren kann dennoch die Authentizitität eines Events sichergestellt werden, da nur die Inhaberin des jeweiligen Schlüsselpaares dieses Event so erstellen konnte. Die Relays sorgen dafür die Daten an die gewünschten Stellen zu bringen und da wir mehr als nur eines benutzen, haben wir eine gewisse Ausfallsicherheit. Da die Daten nur aus signierten JSON-Schnipseln bestehen, können wir sie leicht an einen anderen Ort kopieren, im Falle eines Ausfalls. Durch die Signaturen ist wiederum sichergestellt, dass zwischendurch keine Veränderungen an den Daten vorgenommen wurden.
Beispiel: Ein Nostr Event
Hier ein kleiner technischer Exkurs, der beschreibt, wie Nostr Events strukturiert sind. Falls dich die technischen Details nicht so interessieren, überspringe diesen Abschnitt ruhig.
Jedes Nostr Event besitzt die gleiche Grundstruktur mit den Attributen:
id: Der Hash des Eventspubkey: Der Pubkey des Urhebers des Eventscreated_at: Der Zeitstempel des Eventskind: Der Typ des Eventstags: Zusätzliche Metadaten für das Event können in diesem Array hinterlegt werdencontent: Der textuelle Inhalt eines Eventssig: Die Signatur des Events, um die Integrität der Daten zu überprüfen
json { "id": <32-bytes lowercase hex-encoded sha256 of the serialized event data>, "pubkey": <32-bytes lowercase hex-encoded public key of the event creator>, "created_at": <unix timestamp in seconds>, "kind": <integer between 0 and 65535>, "tags": [ [<arbitrary string>...], // ... ], "content": <arbitrary string>, "sig": <64-bytes lowercase hex of the signature of the sha256 hash of the serialized event data, which is the same as the "id" field> }Die verwendeten Eventtypen sowie die existierenden Spezifikationen lassen sich unter https://github.com/nostr-protocol/nips/ einsehen.
Wichtig ist auch: Du kannst einfach anfangen, Anwendungen zu entwickeln. Die Relays werden alle Events akzeptieren, die dem o.g. Schema folgen. Du musst also niemanden um Erlaubnis fragen oder warten, bis deine Spezifikation akzeptiert und hinzugefügt wurde.
You can just build things.
Exkurs: Nostr für Binärdaten - Blossom
Ja, aber... das ist doch nur für textbasierte Daten geeignet? Was ist denn mit den Binärdaten (Bilder, Videos, PDFs, etc)
Diese Daten sind oft recht groß und es wurde sich auf das Best-Practice geeignet, diese Daten nicht auf Relays abzulegen, sondern einen besser geeigneten Publikationsmechanismus für diese Datentypen zu finden. Der Ansatz wird als "Blossom - Blobs stored simply on mediaservers" bezeichnet und ist recht unkompliziert.
Blossom Server (nichts anderes als simple Medienserver) nutzen Nostr Schlüsselpaare zur Verwaltung Identitäten und zum Signieren von Events. Die Blobs werden über ihren sha256 Hash identifiziert. Blossom definiert einige standardisierte Endpunkte, die beschreiben wie Medien hochgeladen werden können, wie sie konsumiert werden können usw.
Die Details, wie Authorisierung und die jeweiligen Endpunkte funktionieren, werden in der genannten Spezifikation beschrieben.
Nostr 🤝 Öffentliche Bildungsinfrastrukturen
Wie könnten Herausforderungen gelöst werden, wenn wir Nostr als Basis für die öffentliche Bildungsinfrastruktur einsetzen?
Material-Upload
- Es ist nicht einfach möglich OER bereitzustellen, sodass es auch auf verschiedenen Plattformen gefunden werden kann.
Mit Nostr als Basis-Infrastruktur würden die Metadaten und die Binärdaten nicht an den Service gekoppelt sein, von dem aus sie bereitgestellt wurden. Binärdaten können auf sogenannten Blossom-Servern gehostet werden. Metadaten, Kommentare und weitere textbasierte Daten werden über die Relay-Infrastruktur verteilt. Da Daten und Service entkoppelt sind, können die OER Materialien von verschiedenen Anwendungen aus konsumiert werden.
Kuration
- Es gibt keine interoperablen Sammlungen
- Metadaten-Annotation ist zentralisiert
- User können keine eigenen Metadaten hinzufügen
Sammlungen sind per se interoperabel. Auf Protokollebene ist definiert, wie Listen funktionieren. Die Annotation mit Metadaten ist an keiner Stelle zentralisiert. Das Versprechen der RDF-Community "Anyone can say anything about any topic" wird hier verwirklicht. Ich muss mir ja nicht alles anhören. Vielleicht konsumiere ich nur Metadaten-Events bestimmter Redaktionen oder User. Vielleicht nur diejenigen mit einer Nähe zu meinem sozialen Graphen. Jedenfalls gibt es die Möglichkeit für alle User entsprechende Metadaten bereit zu stellen.
Crawling, Indexierung und Suche * An vielen Stellen wird Content doppelt erschlossen, aber immer für die eigene Plattform * Es gibt keinen geteilten Datenraum, in den Akteure Content "pushen" können * Es gibt keine plattformübergreifenden Suchmöglichkeiten
Keine Doppelerschließungen mehr. Wenn ein User im Netzwerk ein Metadatenevent veröffentlicht hat, ist es für alle konsumierbar. Der Datenraum ist per se geteilt. Plattformübergreifende Suche wird durch die Kombination aus Relays und NIPs ermöglicht. In den NIPs können spezielle Query-Formate für die jeweiligen NIPs definiert werden. Relays können anzeigen, welche NIPs sie untersützten. Eine plattformübergreifende Suche ist im Nostr eine relay-übergreifende Suche.
Plattformübergreifende Kollaboration
- Obwohl nun #OEP in aller Munde sind, gibt es keine technischen Ansätze, wie (plattformübergreifende) Kollaboration technisch abgebildet werden kann
Nostr ist der technische Ansatz.
KI-Services
- KI-Services funktionieren oft nur auf der Plattform für die sie entwickelt werden
Es gibt im Nostr das Konzept der Data Vending Machines (s. auch data-vending-machines.org). Statt also einfach nur eine API zu bauen (was auch schon sehr schön ist, wenn sie offen zugänglich ist), könnten diese Services auch als Akteure im Nostr Netzwerk fungieren und Jobs annehmen und ausführen. Die Art der Jobs kann in einer Spezifikation beschrieben werden, sodass die Funktionsweise für alle interessierten Teilnehmer im Netzwerk einfach nachzuvollziehen ist.
Die Services könnten sogar monetarisiert werden, sodass sich hier auch Möglichkeiten böten, Geschäftsmodelle zu entwickeln.
Fazit
Die Open Education Community ist großartig. Es sind einzigartige und unglaublich engagierte Menschen, die sich dem hehren Ziel "Zugängliche Bildung für Alle" -> "Offene Bildung" verschrieben haben. Wir verwenden Creative Commons Lizenzen -> Commons -> Gemeingüter. Es ist okay, dass viele Projekte von Sponsoren und Förderungen abhängig sind. Was wir machen, ist im Sinne eines Gemeingutes: Öffentliche Bildung für alle. Also zahlen wir als Gemeinschaft alle dafür.
Was nicht okay ist: Dass das, wofür wir alle gezahlt haben, nach kurzer Zeit nicht mehr auffindbar ist. Dass es eingeschlossen wird. In öffentlich finanzierten Datensilos. Es muss für alle auch langfristig verfügbar sein. Sonst ist es nicht zugänglich, nicht offen. Dann ist das O in OER nur ein Label und Marketing, um für eine ABM-Maßnahme 3 Jahre Geld zu bekommen. Denn nichts anderes ist Content-Entwicklung, wenn der Content nach drei Jahren weggeschmissen wird.
Und dasselbe gilt für OEP. Offene Lernpraktiken, sind auch nur eine Phrase, wenn wir die passende technische Infrastruktur nicht mitdenken, die wirkliche Offenheit und Kollaboration und damit die Umsetzung offener Lernpraktiken ermöglicht.
Und wenn wir uns jetzt nicht Gedanken darüber machen, die Infrastruktur für offenes Lernen anzupassen, dann werden wir vermutlich in einigen Jahren sehen können, was bei politischen Umorientierungen noch davon übrig bleiben wird. Wenn die Fördertöpfe komplett gestrichen werden, was bleibt dann übrig von dem investierten Geld?
Wir brauchen Lösungen, die engagierte Communities weiter betreiben können und denen kein Kopf abgeschlagen werden kann, ohne dass wir zwei neue daneben setzen könnten.
Wir müssen uns jetzt Gedanken darüber machen.
Wie offen will öffentliche Bildungsinfrastruktur sein?
-
 @ d5c440ce:04726d89
2025-06-05 06:19:49
@ d5c440ce:04726d89
2025-06-05 06:19:49Effektiv behandling af blodsprængninger kræver en professionel tilgang og de rette metoder. Hos Klinik Zenit tilbyder vi skånsomme og dokumenterede teknikker til at reducere synligheden af blodsprængninger i ansigt og på krop. Vores behandlinger tilpasses individuelt og udføres af erfarne specialister med fokus på sikkerhed og langvarige resultater. Få vejledning om hudpleje før og efter behandlingen for at opnå det bedste resultat. Kontakt Klinik Zenit for en professionel vurdering og behandlingsplan.
-
 @ fbf0e434:e1be6a39
2025-06-05 14:06:35
@ fbf0e434:e1be6a39
2025-06-05 14:06:35Hackathon 概要
Verifiable AI Hackathon 由 cheqd 主办,聚焦通过安全、可验证的道德系统构建可信 AI 生态。活动吸引 278 名开发者参与,共提交 21 个项目,致力于推动可信 AI 环境的建立。开发者针对 AI 技术滥用问题(如 deepfake 欺诈)及透明化、道德化 AI 系统构建挑战提出解决方案。
参与者围绕自主经济、AI 验证、安全数据应用等主题,借助 cheqd 的去中心化标识符(DID)与可验证凭证(VC)技术展开探索。核心成果包括内容认证创新方案,以及通过验证数据集防范虚假信息的应用实践。
本次黑客松凸显了 AI 解决方案需以透明度和用户权益为核心的发展方向,旨在通过区块链工具为开发者赋能,夯实安全可靠的 AI 应用基础。这一举措致力于将数字身份与 AI 的交互模式,升级为兼顾可持续性与隐私保护的新型范式。
Hackathon 获奖者
AI Agents 奖项获奖者
- Kith: 这个去中心化系统利用加密的可验证凭证,通过去中心化标识符(DIDs)确保 AI 代理的隐私、认证和可信度。
- Identone: 该项目通过在电话交谈中验证身份来保障人与AI语音代理之间的互动可信度。
- SNAILS.: 利用去中心化数字身份来验证内容的机器人,从而增强 AI 环境中的信任。
其他奖项获奖者
- CheqDeep: 利用区块链技术认证媒体内容,通过 DID 链接资源验证人类来源和真实性。
- Trusty Bytes: 为 AI 代理提供一个获取经过验证数据的市场,使用基于区块链的验证来确保可信交易。
- crdbl: 一个平台,通过可验证凭证、去中心化身份、加密签名和AI验证来提升在线可信度。
构建一个整合私人用户数据的Agent奖项获奖者
- Viskify: 一个AI辅助手的平台,用于人才验证,利用可验证凭证和确定性去中心化标识符,并与 Stripe 和 Verida 集成以进行账单和私人数据管理。
有关所有项目的更多信息,请访问 The Verifiable AI Hackathon。
关于主办方
cheqd
cheqd 是区块链行业的重要参与者,专注于数字身份解决方案。该组织以其在建立支持安全和注重隐私数据管理的去中心化身份基础设施中所扮演的角色而闻名。通过利用最前沿的区块链技术,cheqd 在身份生态系统的标准开发中发挥了关键作用。其努力包括建立战略合作伙伴关系,以创建可互操作的身份服务。秉承加强数字信任框架的承诺,cheqd 继续通过先进且有效的身份管理解决方案来赋能个人和组织。
-
 @ 05a0f81e:fc032124
2025-06-05 18:36:08
@ 05a0f81e:fc032124
2025-06-05 18:36:08Akhenaten (originally named Amenhotep IV) was a pharaoh of ancient Egypt known for radically transforming Egyptian religion, art, and culture. He is most famous for promoting the worship of one god—Aten, the sun disk—marking one of the earliest recorded movements toward monotheism.
Early Life and Rise to Power of pharaoh Akhenaten.
The Birth Name was Amenhotep IV, and he was born Around 1380 BCE. By Pharaoh Amenhotep III, and the mother Likely Queen Tiye. He grew up and married a Wife, Nefertiti, one of Egypt's most iconic queens. He have children, Including daughters and likely the father of Tutankhamun (King Tut).
Amenhotep IV ascended the throne around 1353 BCE, succeeding his father, a powerful and prosperous pharaoh, and there was a Religious Revolution.
A Shift Toward Monotheism
Around his 5th regnal year, Amenhotep IV changed his name to Akhenaten, meaning "Effective for Aten".
He abandoned the traditional Egyptian pantheon, especially the powerful god Amun, and elevated Aten as the sole god.
This was a dramatic break from Egypt's deeply rooted polytheistic religion.
The capital city Akhetaten (Modern-day Amarna). Akhenaten moved the capital from Thebes to a new city he built from scratch: Akhetaten (Horizon of Aten).
The city was dedicated entirely to the Aten religion and became a center of art, culture, and politics.
Nefertiti was not just a queen but a powerful co-ruler. Some theories suggest she may have ruled independently for a time after Akhenaten’s death (possibly as Neferneferuaten).
They had at least six daughters. The identity of Akhenaten's sons is debated, but Tutankhamun is widely believed to be his son, possibly by a secondary wife.
Decline and Death
Akhenaten died around 1336 BCE after a 17-year reign.
After his death, his successors (including Tutankhamun) restored traditional religion, abandoned Atenism, and moved the capital back to Thebes.
His monuments were defaced, and his name was erased from king lists, a process known as damnatio memoriae (damnation of memory).
Legacy
Akhenaten is remembered as:
A visionary who introduced monotheism before it appeared in other cultures.
A heretic who defied over a thousand years of religious tradition.
A reformer whose bold changes caused cultural upheaval.
His religious revolution was short-lived, but modern historians and archaeologists regard him as one of the most fascinating and controversial figures in ancient history.
The reasons why Pharaoh Akhenaten introduced monotheism, the worship of Aten, the sun disk, as the one true god are still debated by historians, but several key political, religious, personal, and philosophical factors likely contributed.
✅ Main Reasons Why Akhenaten Introduced Monotheism
- Religious Reform: Belief in a Universal Power
Akhenaten may have genuinely believed in Aten as the supreme creator and life-giver.
The sun was already important in Egyptian religion (Ra, Amun-Ra), but Akhenaten stripped away all personification, choosing the sun's disk (Aten) as a pure, abstract symbol of divine power.
He saw Aten as omnipresent, providing light and life to everything and everyone equally.
- Political Motivation: Weaken the Power of the Priests
The priesthood of Amun at Thebes had become extremely wealthy and powerful, almost a state within a state. By elevating Aten and banning Amun's worship, Akhenaten dismantled the influence of the Amun priests and centralized religious power in his own hands. He made himself the sole mediator between Aten and the people, increasing royal control.
- Personal Vision and Identity
Akhenaten may have had a personal religious experience or conviction that shaped his devotion to Aten.
His new name, “Akhenaten,” meaning “Effective for the Aten,” reflects a deep, personal connection to this god.
He often depicted himself and his family in direct contact with Aten, showing a highly intimate and unique belief system.
- Philosophical and Artistic Shift
Akhenaten's reign saw a revolution in art, emphasizing naturalism, emotion, and individuality.
This change in thinking may reflect a broader philosophical shift toward a more abstract and spiritual understanding of the divine unified in Aten.
Atenism removed the idea of gods with human forms, replacing them with a universal force (the sun's light).
- Reaction Against Religious Corruption or Complexity
Traditional Egyptian religion had hundreds of gods, rituals, and temple hierarchies.
Akhenaten may have seen the system as corrupt, ritualistic, and too complex for ordinary people.
Atenism was simple, focused, and accessible, with the sun’s light reaching everyone equally.
- Political Instability or Health Issues (Speculative)
Some theories suggest Akhenaten’s appearance (depicted with elongated head, wide hips, etc.) may reflect a genetic disorder (e.g., Marfan syndrome or Froehlich's syndrome).
If he was sickly, he may have been drawn to religious introspection or spiritual reform.
Others suggest that political instability or unrest during his early reign may have motivated a bold unifying reform.
Summary
Akhenaten’s monotheism was unprecedented in Egypt’s long religious history. Whether he was a spiritual visionary, a political tactician, or both, his religious revolution stands out as one of the most dramatic and controversial in ancient history.
-
 @ 04c915da:3dfbecc9
2025-03-26 20:54:33
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 527337d5:93e9525e
2025-06-05 03:09:02
@ 527337d5:93e9525e
2025-06-05 03:09:02The Algorithmic Pursuit of Connection: A Five-Book Journey into the Self
As a researcher, hitting my thirties and the winding down of a significant project prompted a crucial re-evaluation of life's latter half. While I'd successfully applied probabilistic control theory to one-on-one interactions, the complexities of group dynamics remained a persistent challenge. My recent dive into five diverse books on human relationships inadvertently became a profound journey of self-discovery, fundamentally reshaping my perspective on social connections.
Neil Strauss: A Mirror Reflecting the Self's Evolution
Neil Strauss's The Truth resonated deepest among my recent reads. The author's battle with sex addiction uncomfortably mirrored my own past struggles: the fragile self-esteem stemming from rejection, the hubris born of early successes, and the tendency to view women as mere objects of manipulation. It felt eerily prescient, a glimpse into a potential future.
Yet, I found myself arriving at Strauss's ultimate conclusion – the paramount importance of self-preparation and community – far sooner than he did. This acceleration wasn't accidental; it was the result of intense focus on individual experiences, meticulously replayed and analyzed in my mind. The book, therefore, served less as a revelation and more as a powerful validation of my own journey of introspection and root-cause analysis.
Quantifying Connection: The Promise and Limits of Mathematical Models
Hannah Fry's The Mathematics of Love offered a kindred spirit in its attempt to quantify human relationships. While I appreciate the mathematical lens, Fry's models primarily concern dyadic relationships (N=2), relying on relatively simple systems of two-variable ordinary differential equations. For me, these are akin to linear models, sufficient only up to a certain point. Beyond N=4, the dependencies become exponentially complex.
My own pursuit extends to understanding and optimizing group dynamics within complex systems. This involves multi-variable problems (N $\ge$ 3) and the application of network theory, a far more sophisticated approach. Human collectives, after all, are systems of nodes and edges, where information propagates in predictable ways. My focus is on deriving optimal behavioral controls within these intricate frameworks.
Conversely, Men Are from Mars, Women Are from Venus initially struck me as bordering on conspiracy theory. However, its latter half proved unexpectedly useful. Its clear enumeration of male and female desires, and its articulation of common points of conflict, presented a practical template for communication styles. In a systemic view, this serves as a rudimentary, yet functional, interface design for complex social interactions.
A Dispassionate Critique of Relationship Dogma
My drive for efficiency and systematic understanding led to a rather blunt assessment of certain relationship classics. The New Science of Adult Attachment felt disorganized and frustratingly anecdotal. Lacking a coherent theoretical framework, it burdened the reader with deciphering meaning from a jumble of examples. Its inefficiency was, frankly, its most irksome flaw.
Similarly, Dale Carnegie's How to Win Friends and Influence People struck me as closer to pseudoscience than social science. Its plethora of specific anecdotes obscured any underlying principle. Given my deep engagement with social engineering – a discipline that systematically and practically analyzes human interaction – Carnegie's work appeared largely irrelevant and inefficient. From my perspective, which views humans as objective systems to be analyzed with mathematical rigor, such unstructured approaches hold little value.
The Unveiling of a Core Principle: Humans as Systems
This intensive reading period solidified my most crucial insight: humans, at their core, are systems. This understanding allows for a dispassionate, methodical approach to human collectives, mitigating unnecessary emotional friction.
This revelation has sharply refined my future learning trajectory. I'm now prioritizing foundational theories like graph theory and network theory over anecdotal accounts of human behavior. By mastering these theoretical underpinnings, I aim to precisely model complex human interactions as systems of nodes and edges, enabling the derivation of optimal behavioral controls within communities.
My choice of the term "target for capture" for individuals stems from a personal aversion to perceived equality in certain human interactions, a mechanism to avoid cognitive dissonance. This rational approach, I believe, is key to cultivating secure attachment styles – relationships demonstrably sustainable in the long term. My philosophy is to strategically approach the initial engagement, then transition to a stable, enduring connection. It's a calculated, dispassionate method for achieving desired relational outcomes.
Ultimately, this period of reading wasn't just about acquiring knowledge; it was a profound journey of self-discovery, clarifying my personal frameworks for navigating life's complexities and forging meaningful, yet strategically managed, connections.
-
 @ a5142938:0ef19da3
2025-06-05 10:24:37
@ a5142938:0ef19da3
2025-06-05 10:24:37Brands
Nordkidz is a German brand that creates made-to-order clothing and linens for babies, children, and a little bit for their parents.
Natural materials used in products
⚠️ Warning: some products from this brand contain non-natural materials, including:
Categories of products offered
This brand offers products made entirely from natural materials in the following categories:
Clothing
- Clothing fits : babies, children, unisex
- Tops : sweaters, t-shirts
- Bottoms : pants-trousers, shorts, sweatpants
- Head & handwear : hats, scarves
Home
- Linen : bath ponchos, bean bag covers, muslin squares
Other information
👉 Learn more on the brand website
Where to find their products?
- Nordkidz (in German, delivery area: Germany and the European Union) 💚 Via this link, you directly support the brand.
📝 You can contribute to this entry by suggesting edits in comments.
🗣️ Do you use this brand's products? Share your opinion in the comments.
⚡ Happy to have found this information? Support the project by making a donation to thank the contributors.
-
 @ 04c915da:3dfbecc9
2025-03-10 23:31:30
@ 04c915da:3dfbecc9
2025-03-10 23:31:30Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Usually stolen bitcoin for the reserve creates a perverse incentive. If governments see a bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 04c915da:3dfbecc9
2025-03-07 00:26:37
@ 04c915da:3dfbecc9
2025-03-07 00:26:37There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ 49d472c1:a63cd544
2025-06-05 02:59:12
@ 49d472c1:a63cd544
2025-06-05 02:59:12Bitcoin Miners Pivot to Power AI Boom, Offering a Lifeline to America’s Data-Center Crunch
A fresh Morgan Stanley analysis warns that U.S. data-center demand will balloon to ≈65 GW between 2025 and 2028—about 45 GW more than the grid can currently supply. One solution the bank singles out: repurposing the oversized, transformer-fed campuses originally built for Bitcoin mining. (investopedia.com)
Several public miners are already moving. Riot Platforms has begun buying extra land near its Corsicana, TX complex and hired a veteran data-center executive to head a “high-performance compute” division aimed squarely at AI customers. (riotplatforms.com, coindesk.com) Bitfarms, meanwhile, is marketing North-American sites to hyperscalers after hiring consultants to evaluate GPU-ready retrofits. (reuters.com)
Industry analysts say the pivot is existential. April 2024’s fourth halving chopped block rewards to 3.125 BTC, shrinking miner revenue just as network difficulty hit record highs. By leasing idle megawatts—or fully converting halls—operators lock in dollar-denominated cash-flows while retaining the option to resume mining if margins rebound.
“Miners spent the last cycle amassing land, switchgear and transformers. AI is about to pay them for it.” —Greg Miller, Citizens JMP (research note quoted in multiple sector briefings)
Why it matters
- Grid relief: Every gigawatt shifted from speculative hashing to AI compute eases ERCOT’s peak-load stress and shortens transmission-upgrade timelines. (datacenterdynamics.com)
- Cap-ex savings for cloud firms: Retrofitting a mining hall is months faster—and currently 30-40 % cheaper—than green-field construction, analysts estimate. (govtech.com)
- Dual-revenue model: Miners keep upside to future BTC price spikes while monetizing power capacity today.
The roadblocks
- Cooling retrofits: Air-cooled ASIC barns must be re-engineered for liquid-cooled GPU clusters, at up to \$3 M per MW in conversion costs. (driehaus.com)
- Policy risk in Texas: Lawmakers are weighing caps on industrial load-flex credits after recent grid-stress events, which could dent miners’ ancillary revenue. (dallasnews.com)
Bottom line: Once-beleaguered Bitcoin mines may become critical real estate for the surging AI sector—turning yesterday’s crypto boomtowns into tomorrow’s compute hubs while giving miners a much-needed new income stream.
-
 @ 04c915da:3dfbecc9
2025-03-04 17:00:18
@ 04c915da:3dfbecc9
2025-03-04 17:00:18This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ 04c915da:3dfbecc9
2025-02-25 03:55:08
@ 04c915da:3dfbecc9
2025-02-25 03:55:08Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 42a071ab:3391e086
2025-06-05 09:31:56
@ 42a071ab:3391e086
2025-06-05 09:31:56Trong một thế giới mà sự cạnh tranh ngày càng khốc liệt, yếu tố tạo nên sự khác biệt không chỉ nằm ở chất lượng sản phẩm mà còn ở cách một thương hiệu chăm sóc và kết nối với khách hàng. AV88 hiểu rõ điều đó và đã không ngừng đầu tư vào trải nghiệm người dùng như một chiến lược cốt lõi để xây dựng lòng tin và sự trung thành. Ngay từ những bước đầu tiên khi khách hàng tiếp cận AV88, họ được đón nhận bởi một giao diện thân thiện, dễ sử dụng và được thiết kế dựa trên hành vi sử dụng thực tế. Tất cả các chức năng, từ đăng ký tài khoản, quản lý thông tin cá nhân cho đến các bước tương tác hằng ngày đều được tối ưu để đảm bảo sự liền mạch và thuận tiện. Hơn thế, AV88 còn xây dựng một hệ thống chăm sóc khách hàng luôn sẵn sàng hỗ trợ 24/7, cung cấp thông tin kịp thời và giải quyết mọi thắc mắc nhanh chóng, mang lại cảm giác yên tâm tuyệt đối cho người sử dụng. Không chỉ dừng lại ở mức độ phản hồi, đội ngũ tại AV88 còn chủ động thu thập ý kiến, khảo sát nhu cầu và cải tiến dịch vụ theo thời gian thực, từ đó đảm bảo rằng mỗi sự đổi mới đều xuất phát từ chính kỳ vọng của người dùng. Nhờ vậy, AV88 không đơn thuần là một nền tảng dịch vụ mà còn là một người bạn đồng hành đáng tin cậy trong hành trình số hóa của mỗi khách hàng.
av88 cũng đặt ra một tiêu chuẩn mới cho sự minh bạch và bảo mật – hai yếu tố then chốt trong việc xây dựng niềm tin lâu dài. Mọi quy trình đều được thiết lập rõ ràng, dễ theo dõi và có hướng dẫn chi tiết, từ quy trình giao dịch cho đến các chính sách bảo vệ thông tin cá nhân. Các công nghệ mã hóa tiên tiến và lớp xác thực đa tầng giúp bảo đảm an toàn tuyệt đối trong mọi hoạt động. Không dừng lại ở việc duy trì chất lượng dịch vụ, AV88 còn tiên phong trong việc tích hợp công nghệ nhằm tối ưu hóa hiệu suất và giảm thiểu thời gian chờ đợi của người dùng. Các thao tác nạp – rút nhanh chóng, hệ thống thông báo thông minh và tính cá nhân hóa trong trải nghiệm giúp người dùng cảm nhận được sự linh hoạt và chuyên nghiệp. Chính sự kết hợp giữa công nghệ, con người và tầm nhìn chiến lược đã giúp AV88 không chỉ duy trì vị thế trên thị trường mà còn định hình chuẩn mực mới cho ngành dịch vụ lấy khách hàng làm trung tâm. Dù trong bối cảnh nào, AV88 vẫn luôn giữ vững cam kết: lắng nghe, thấu hiểu và đồng hành cùng khách hàng trên mọi hành trình. Điều này không chỉ tạo dựng giá trị bền vững cho thương hiệu mà còn góp phần nâng cao tiêu chuẩn chung của ngành, thúc đẩy sự phát triển toàn diện và dài lâu.
-
 @ de7306de:1ea53f87
2025-06-05 08:46:54
@ de7306de:1ea53f87
2025-06-05 08:46:54Être « de gauche » ?
Essai pour une (re)définition transversale des concepts « gauche » et « droite »
Introduction
Il y a toujours deux niveaux. Le premier est celui sur lequel on s’appuie quand on se dit « de gauche » : c’est le niveau du discours, des bonnes intentions, des objectifs ou des revendications bien rationnelles, des belles valeurs, des symboles, des vérités chéries, etc. Puis il y a l’autre niveau, moins conscient, voire inconscient, qui fait que l’on va finir par réagir d’une certaine manière, parfois, souvent, en contradiction avec le premier niveau. Ce n’est pas, par exemple, parce qu’on n’aime pas la jalousie ou le pouvoir qu’on ne va pas se sentir jalouses ou qu’on ne va pas, parfois, prendre du plaisir dans certaines dynamiques de pouvoir. Combien de fois nous sommes-nous retrouvées frustrées de voir à quel point la réalité de nos actions se déroule en totale contradiction avec nos intentions ? Et ce, dans tous les domaines de la vie : intime, amoureuse, amicale, professionnelle, militante, etc. C’est-à-dire que nous pouvons être très « de gauche » au niveau des intentions, mais réactionnaires, voire fascistes, au niveau des pratiques. C’est donc ce deuxième niveau, dominé non pas par la raison, les concepts, les manifestes ou les bonnes intentions, mais par le monde inconscient, ses flux et ses mécanismes, auquel nous allons nous intéresser, car c’est bien là que la question se joue. Nous proposons donc un ensemble de prismes (Δ), sans aucune prétention totalisante, pour contribuer à une (ré)définition collective des concepts de gauche et de droite.
1er prisme Δ
Sensibilités et compétences
S e n s i b i l i t é :
propriété / aptitude d’une matière, d’un organe, d’un corps à réagir aux stimuli externes ou internes.
Le mot sensibilité vient de sens. Les sens captent. On peut réagir seulement aux stimuli/informations que l’on capte – inutile de forcer un aveugle à voir, un sourd à entendre. Les yeux captent la lumière, les tympans captent des ondes/vibrations. Or, il ne suffit pas d’avoir de bons yeux et de bonnes oreilles pour capter, par exemple, l’injustice dans notre entourage. Il nous faut quelque chose de plus. Quelque chose d’autre que nos sens physiologiques est à l’œuvre dans nos esprits lorsqu’on capte une injustice. Comme s’il y avait un autre type de sens. Si les sens physiologiques captent les informations physiques (lumière, vibration, température, distance, etc.), cet autre type de sens capte les informations sociales (quelle est ma place dans la meute, quand est-ce mon tour de manger, quel territoire m’est attribué ? etc.). Si, pour les sens physiologiques, des récepteurs chimiques et des terminaisons nerveuses sont à l’œuvre, pour cet autre type de sens, il s’agit plutôt de programmes, de « logiciels », un peu comme les applications de nos téléphones portables ou de nos ordinateurs. Il y a donc des « logiciels » qui nous permettent de capter les injustices, les violences, les oppressions, les signes de souffrance, de maladie, de dépression, de névrose ou de psychose, etc. Inutile de forcer un aveugle à voir, inutile de forcer quelqu’un qui n’aurait pas les bons logiciels à capter une injustice, une violence, une oppression. Il ne s’agit donc pas de vouloir ou de décider de capter ces situations ou ces phénomènes sociaux, il s’agit d’avoir, de cultiver les « bons logiciels ». Voilà donc ce à quoi nous nous référons quand on parle de sensibilités. Être de gauche donc, selon ce prisme, n’est pas tellement une décision, un vouloir ou une sorte d’identité autoproclamée que l’on pourrait rajouter facilement dans nos CV, afficher sur nos réseaux sociaux ou sur nos applis de rencontre, montrer avec nos t-shirts du Che Guevara, avec nos chants anarchistes ou nos quelques actions, non, non, non. Être de gauche = être sensible. Multi-sensible, pluri-sensible. Mais sensible à quoi ? À une diversité de phénomènes concernant le mental, le social et l’environnemental – et spécialement à leur intrication. Être de gauche implique donc avoir cultivé dans nos esprits une multiplicité de sensibilités : des sensibilités psychologiques, sociologiques, anthropologiques, écologiques… De ce point de vue, être de gauche n’est pas un discours, une mode, une décision, une envie, c’est du travail ! Car cette multiplicité de sensibilités, nous ne la cultivons pas par défaut socialement, culturellement – la société industrielle, capitaliste qui nous a façonnés, n’a surtout pas besoin d’esprits pluri-sensibles. Nous sommes obligés donc, si nous voulons cultiver ces sensibilités, de nager à contre-courant, de lutter contre le cadrage et la parcellisation propres à nos sociétés modernes, consistant à produire de petits soldats, de petits robots, de petites machines spécialisées, chacune dans son champ spécifique, et ce pour servir à qui ? Surtout pas à nous-mêmes, que ce soit individuellement ou collectivement. Nous voyons bien que ce n’est pas une mince affaire d’« être de gauche ». Quelque part, personne n’est de gauche, puisque personne n’est en mesure, prenant en compte la façon dont notre culture produit des sujets, d’avoir tout cet éventail de sensibilités. Pour mieux nuancer la question, nous sommes obligés de laisser de côté les lunettes de l’être, car elles nous contraignent à aborder le sujet de façon binaire : être ou ne pas être, soit tu es de gauche, soit tu ne l’es pas. On voit très bien que nous pouvons être sensibles par rapport à un sujet, à une situation ou à un domaine spécifique et, en même temps, très insensibles par rapport à d’autres sujets, situations ou domaines. Oui, cela veut dire que nous sommes de gauche et aussi, en même temps, de droite (insensibles) selon les endroits que l’on observe en nous, dans diverses situations et contextes. Il ne suffit pas d’« être marxistes » ou d’« être anarchistes » pour ne pas devenir des grands ou des petits tyrans, des grands ou des petits colons, des sexistes, des racistes, des oppresseurs des minorités, des validistes, des violents, des agresseurs, que ce soit au niveau collectif ou sur un niveau plus personnel, plus intime. De droite et de gauche, en même temps ? Quelle idée ! C’est que « être de gauche » est une expression trop rigide. Il convient donc d’analyser la question en termes de devenir : si l’être est un état donné, une pierre, le devenir représente toujours le mouvement, le fleuve et ses tourbillons. Nous serions très prétentieux, très arrogants ou très naïfs, si nous disions que nous sommes de gauche. En revanche, nous pouvons dire sans aucune prétention que nous sommes dans un devenir de gauche, dans la mesure où l’on cultive les sensibilités diverses. Nous avons dit qu’être de gauche veut dire être multi-sensible ; que nous ne pouvons pas vraiment être de gauche, car malgré le fait que l’on soit sensibles à certains sujets ou situations, nous sommes forcément insensibles par rapport à d’autres sujets et à d’autres situations, car victimes de l’industrie et de son culte des œillères ; que nous sommes en même temps de gauche et de droite, selon les endroits que l’on observe en nous dans une situation donnée, dans un contexte donné ; que le prisme du devenir est plus adapté que les lunettes de l’être, et qu’au lieu de dire « je suis de gauche », il est plus précis de dire « je suis dans un devenir ‘de gauche’ ».
Compétences ?
Nous avons, jusqu’à maintenant, abordé la question de la gauche en ce qui concerne les sensibilités, c’est-à-dire la captation des signes ou des informations concernant le mental, le social et l’environnemental. Mais suffit-il d’être sensible, même multi-sensible ? Combien de fois avons-nous capté des injustices, des conflits et toutes sortes de problèmes par rapport auxquels nous n’avons rien pu faire ? Nous pouvons être très sensibles et en même temps nous sentir très impuissants. Il y a donc deux choses qui seraient précieuses pour la gauche selon ce prisme : la captation et l’action, les sensibilités et les pratiques. Pour faire ou pratiquer, il faut pouvoir faire, être capable, compétent. Faire un bon discours, gérer un conflit, établir des relations de façon saine, produire autrement, consommer autrement, gérer la propriété autrement, apprendre à prendre soin et à nous soigner, apprendre à soutenir des personnes, déconstruire nos vieux logiciels, expérimenter et trouver les modes d’organisation les plus adaptés, articuler les différents terrains d’action politique (macro, micro et infra-personnel), devenir souples et ouverts au monde, à l’altérité, etc. Tout cela requiert à la fois des sensibilités et des compétences très concrètes, précisément celles que la société néglige, que notre culture ne cultive pas. Dans la gauche au sens traditionnel, y compris ladite « extrême gauche » ou « gauche radicale », prenons-nous au sérieux cette question ? Sommes-nous en train de cultiver cette multiplicité de sensibilités et de compétences ?
Et la droite, c’est quoi ?
Nous avions jusqu’à maintenant utilisé ce prisme pour définir la gauche comme sensible, comme multi-sensible. Comment faire alors sens de la droite ? Est-ce l’insensibilité qui la définit ? Les personnes plus à droite sont-elles insensibles ? Nous avions défini la sensibilité comme une sorte de logiciel nous permettant de capter et de réagir à un stimulus, à une information, à une situation donnée. L’acte raciste, classiste, sexiste, n’est-il pas nécessairement la conséquence d’un type de sensibilité, selon notre définition ? Sensibilité par rapport à l’« invasion » de la part des étrangers, au « grand remplacement », aux « déviances » sexuelles ou de genre, à l’« hystérie » des femmes, à l’« insolence » des travailleurs, etc. Nous pourrions dire que la droite est aussi sensible, et même multi-sensible ! Ce constat fait-il effondrer notre propos ? Ou est-ce qu’il y aurait des « bonnes » et des « mauvaises » sensibilités ? Les sensibilités, expliquent-elles vraiment le clivage gauche-droite ? Nous considérons qu’au contraire, notre propos tient très bien. Pour nous, la droite s’explique en termes d’insensibilité et aussi en termes de sensibilité. D’abord d’insensibilité, car la droite est insensible à une diversité de phénomènes, à un ensemble d’injustices, de violences et d’oppressions, et en même temps, elle se définit par un ensemble de sensibilités que nous pourrions qualifier d’inadaptées. Il y aurait donc des sensibilités adaptées et des sensibilités inadaptées selon la situation, selon le contexte. Mais adaptées ou inadaptées selon quels critères, selon quelle science ou quelle philosophie ? Qualifier une sensibilité, un logiciel d’inadapté, n’est-il pas trancher de façon complètement arbitraire dans l’amoralité du cosmos ? Ce problème philosophique n’est pas facile à résoudre sans invoquer une justice divine, un évangile religieux ou un évangile militant. Or, il y a une chose, pour nous la seule, qui tranche la question malgré nous, en dépit de nous, au-delà de nous, en deçà de nous, autour de nous, à travers nous. C’est la vie elle-même, ou plus précisément l’écologie. Tout système « vivant », y compris les rapports sociaux, obéit à des « principes » écologiques : si on ne boit pas assez d’eau, on finit par mourir ; si nous refoulons des émotions, des pulsions vitales, nous serons condamnés à être névrosés, malades ; si nous colonisons un peuple et si, lorsque ce peuple se défend, nous le réprimons violemment, une partie de ce peuple cherchera à se défendre d’une façon plus violente, et si notre réponse à une telle « radicalisation » est de fusiller ou de bombarder les « radicaux », les « terroristes », alors au lieu de diminuer la « menace terroriste » qui nous fait peur, nous sommes en train de la nourrir, le paradoxe étant que c’est nous, avec le premier acte de colonisation, qui l’avons provoquée. Ces trois exemples représentent des réalités, des déterminations écologiques qui n’ont rien à voir avec nos croyances, nos valeurs, nos idéologies, nos symboles. Nous pouvons identifier de mieux en mieux quand un écosystème comme une forêt est perturbé, troublé, malade ou menacé de mort. C’est l’interrelation de fonctions en équilibre(s) qui fait forêt. Tout ce qui perturbe, trouble ou menace ces équilibres est considéré comme toxique, comme nocif, comme maladif. Cela semble évident pour la forêt, or nous devons souligner que l’esprit humain ainsi que les sociétés humaines obéissent aux mêmes types de déterminations écologiques. Ces déterminations sont elles-mêmes déterminées par la singularité de chaque écosystème : il y a des forêts qui ont moins besoin d’eau, de chaleur et de lumière que d’autres, c’est d’ailleurs ce qui différencie la forêt de la jungle. Et il y a aussi des déterminations qui s’appliquent dans toute forêt, dans toute jungle : si les bactéries qui captent l’azote de l’air (N≡N – non assimilable) et qui le fixent dans le sol sous forme d’ammoniac, nitrites et nitrates (·NH3, ·NO2, ·NO3 - assimilables) disparaissent, alors n’importe quelle forêt ou jungle serait condamnée à une mort subite/rapide, car ces bactéries représentent la source d’azote pour la quasi-totalité des êtres vivants, l’azote faisant partie essentielle de l’ADN, leur absence serait fatale – pas d’azote assimilable, pas de vie. Nous considérons que ce sont ces déterminations, générales et singulières, dans chaque registre écologique et dans leur intrication – mental, social et environnemental – qui détermineront les sensibilités adaptées ou inadaptées dans un moment, une situation, un contexte, un territoire donné. Nous pouvons dire alors que les sensibilités de la gauche, ce sont des sensibilités seulement par rapport aux / concernant les trois registres écologiques dans leur intrication, tandis que la droite est précisément insensible aux rapports écologiques, à l’écologie dans ce sens large, et sensible ou hyper-sensible par rapport à ce qui fait inconsciemment peur, à ce qui menace leurs territoires existentiels, et plus précisément leurs points d’accrochage (deuxième Δ), autour desquels ces territoires ont été constitués / formés.
Gauche = sensibilités et compétences qui œuvrent dans le sens écologique – Écosophique : articulation transversale de trois registres écologiques – mental, social et environnemental.
Droite = sensibilités et compétences qui œuvrent dans un sens non-écologique, anti-écologique, écocide.
-
 @ 5d4b6c8d:8a1c1ee3
2025-06-05 01:28:52
@ 5d4b6c8d:8a1c1ee3
2025-06-05 01:28:52How did the stackers do on their ~HealthAndFitness journeys today?
I did very well: Slept well? Check Stuck to fast? Check Ate healthy? Check Activity target? Checkarooni
The one oddity I need to work on is that I got a foot cramp while playing turtle tag with my daughter.
https://stacker.news/items/997476
-
 @ 6e0ea5d6:0327f353
2025-02-21 18:15:52
@ 6e0ea5d6:0327f353
2025-02-21 18:15:52"Malcolm Forbes recounts that a lady, wearing a faded cotton dress, and her husband, dressed in an old handmade suit, stepped off a train in Boston, USA, and timidly made their way to the office of the president of Harvard University. They had come from Palo Alto, California, and had not scheduled an appointment. The secretary, at a glance, thought that those two, looking like country bumpkins, had no business at Harvard.
— We want to speak with the president — the man said in a low voice.
— He will be busy all day — the secretary replied curtly.
— We will wait.
The secretary ignored them for hours, hoping the couple would finally give up and leave. But they stayed there, and the secretary, somewhat frustrated, decided to bother the president, although she hated doing that.
— If you speak with them for just a few minutes, maybe they will decide to go away — she said.
The president sighed in irritation but agreed. Someone of his importance did not have time to meet people like that, but he hated faded dresses and tattered suits in his office. With a stern face, he went to the couple.
— We had a son who studied at Harvard for a year — the woman said. — He loved Harvard and was very happy here, but a year ago he died in an accident, and we would like to erect a monument in his honor somewhere on campus.— My lady — said the president rudely —, we cannot erect a statue for every person who studied at Harvard and died; if we did, this place would look like a cemetery.
— Oh, no — the lady quickly replied. — We do not want to erect a statue. We would like to donate a building to Harvard.
The president looked at the woman's faded dress and her husband's old suit and exclaimed:
— A building! Do you have even the faintest idea of how much a building costs? We have more than seven and a half million dollars' worth of buildings here at Harvard.
The lady was silent for a moment, then said to her husband:
— If that’s all it costs to found a university, why don’t we have our own?
The husband agreed.
The couple, Leland Stanford, stood up and left, leaving the president confused. Traveling back to Palo Alto, California, they established there Stanford University, the second-largest in the world, in honor of their son, a former Harvard student."
Text extracted from: "Mileumlivros - Stories that Teach Values."
Thank you for reading, my friend! If this message helped you in any way, consider leaving your glass “🥃” as a token of appreciation.
A toast to our family!
-
 @ 8c29b321:4336aaa0
2025-06-05 08:32:10
@ 8c29b321:4336aaa0
2025-06-05 08:32:10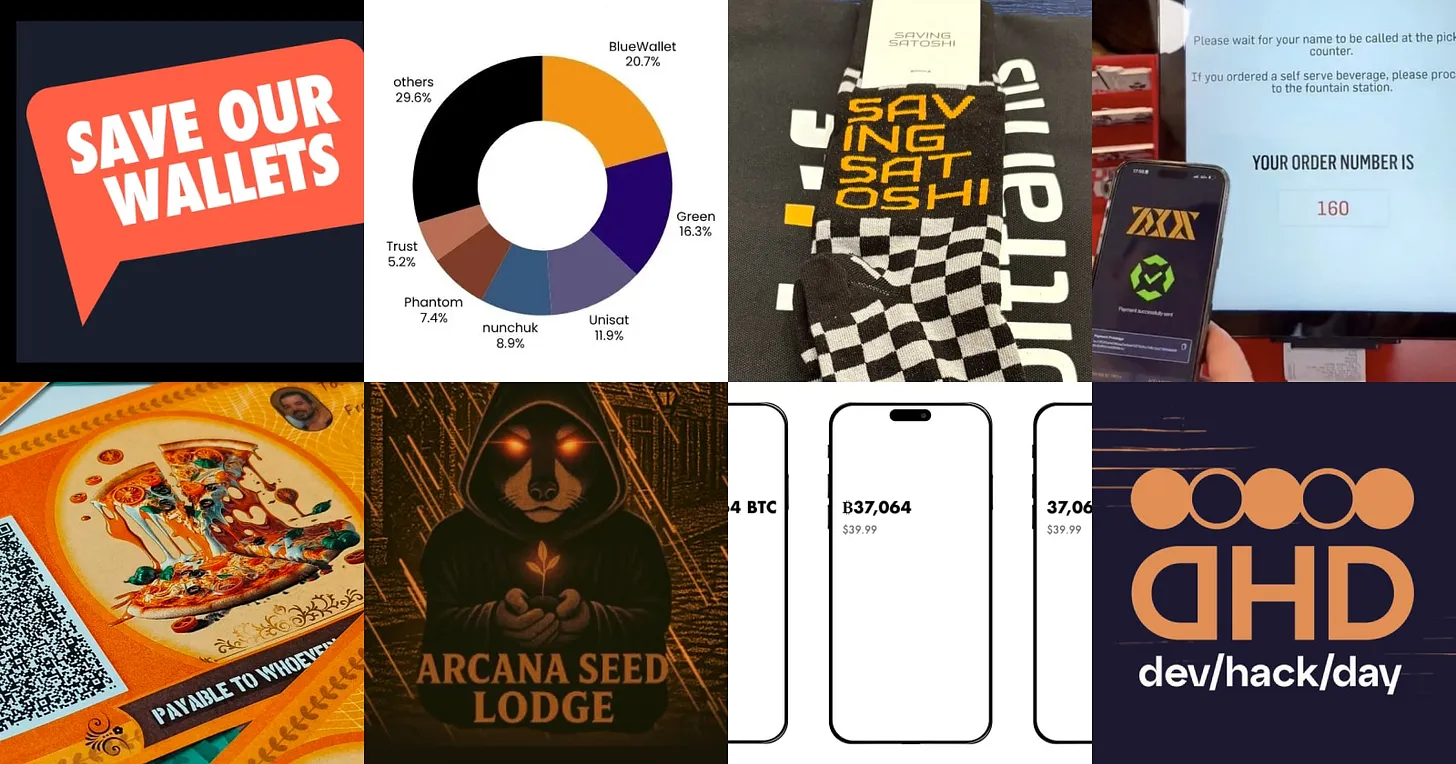
Community 🧑🤝🧑
- Did you see that the Designathon wrapped up? If not, take a peek at the previous newsletter.
- The community conducted research at Oslo Freedom Forum. Bitcoin and Nostr have the potential to provide privacy focussed financial and communication tools for activists. We'll publish findings publicly and host developer workshops to share the insights.
- BTC Prague is coming up from June 18 to 21. Meet up at the design track during dev/hack/day and around the general conference. The aforementioned activist research and Bitcoin Core App are two of the scheduled talks.
- We had an exploratory call about how Liana could implement Payjoins (recording).
- The price for Best Design at the Bitcoin 2025 hackathon, sponsored by the Bitcoin Design Foundation, went to Arcana Seed Lodge. Check out all the projects.
- For anyone in the US, help protect your right to transact freely via Save our Wallets. There’s a bill being discussed around protecting builders of non-custodial wallets and services.
Bitcoin design guide 🗺️
- The intro page to the Getting Started section got a rewrite. Does it read better and is it more informative now?
- The section for visual formatting of addresses was updated with a note about using fonts with clearly distinguishable characters.
- Find new t-shirt designs with bitcoin & design related taglines on the Design files page (Figma community file).
- Would you like to help create an online course around design for Plan₿ Network?
- AI knows the guide and can evaluate your design based on it. How else can we use AI?
Seeking feedback 🗣️👂
- Liana Wallet is interviewing bitcoiners around frustrations with self-custody.
- Yashraj is seeking feedback on UX challenges around Payjoin V2 (outline, Github, Stacker News).
- 0commons is a bitcoin-powered value-for-value marketplace for digital goods. Leave your feedback.
- Kelbs is looking for feedback on home screen designs for Sovrn.
- m1sterc001guy is looking for feedback on a Fedimint wallet prototype (repo).
- There is a lot of activity around bitcoin redenomination (BIP 177), removing the term satoshi as a unit. Join the conversation.
Wallet updates 👜
- An update on Cashu ecosystem developments in Q1 2025.
- Boardwalk Cash is an example for the redenomination of bitcoin units. A live example on how “1 Satoshi” can be displayed as “1 Bitcoin”.
- Wallet of Satoshi is going to release a non-custodial wallet and become available again in the US.
- Akron released a beta wallet with support for the Spaces protocol.
- Blockstream released a new wallet app.
- Sparrow made several accessibility improvements in the 2.2.0 release.
Conferences 📅
- Catch up with the recordings and hackathon winners of the BTC++ Austin conference.
- Watch presentations of the Bitcoin Presidio hackathon finalists.
- Find a more complete list of conferences here.
Opportunities 💡
- BRAIINS is looking for a content Lead.
- Apply to the Bitshala design fellowship.
- Cowbolt is looking for a designer.
Everything else 😀
- HRF is supporting another 22 projects with grants. Take a look.
- Happy Bitcoin Pizza Day!
- Check out Jason’s guide to bitcoin accessibility.
- View survey results around mobile wallet usage in Japan by Diamond Hands.
- The Second team published research around how the Ark network can complement Lightning infrastructure.
- Watch the Freedom Tech track presentations from the Oslo Freedom forum.
- Watch Daniel answer 21 questions in 21 minutes.
- Read Bitcoin testing is a ghost town by AVB (also part two).
- Saving Satoshi did a workshop at the Bitcoin Conference. Have you tried it?
- See the UX of paying for burgers at the US fast-food chain Steak’n Shake.
- A guidepr to Robosats, for private exchange of bitcoin.
- Hear about the latest on Fedimint in this podcast.
- Read about building inclusivity into every phase of a project.
- Check out the Global State of Crypto report by Gemini.
—
For more, visit the Bitcoin Design website and follow us.
This update is brought to you by Christoph & Mo. We’d love to hear your feedback. -
 @ a296b972:e5a7a2e8
2025-06-04 22:06:06
@ a296b972:e5a7a2e8
2025-06-04 22:06:06In dem Video geht es um Dietrich Bonhoeffer, wie er sich zu Dummheit und vorsätzlicher bzw. rationaler Ignoranz geäußert hat. Schon seit einiger Zeit geht bei vielen Seltsames vor: Sie werden mit einem Thema persönlich konfrontiert und postum gibt es genau zu diesem Thema ein Video oder einen Artikel. Das kommt manchmal so vor, wie ein Frage- und Antwort-Spiel innerhalb der Schwarm-Intelligenz. Irgendwie spooky.
Die erschreckende Theorie der Dummheit, die Sie nie hören sollten - Dietrich Bonhoeffer: https://www.youtube.com/watch?v=PH-Vs5ILEko
Dem Entdecken, oder besser, dem Auf-einen-Zukommen, ist dieser E-Mail-Schriftverkehr in zeitlichem Zusammenhang vorausgegangen:
Nachfrage zu einem Aufruf durch einen Mitarbeiter zur Blutspende in einem Unternehmen mit über 100 Mitarbeitern über den E-Mail-Verteiler:
Lieber XXXXXXX,
danke zunächst für Dein Engagement.
In meiner näheren Familie gibt es jemanden, der regelmäßig Blut spendet, daher bin ich ein wenig für das Thema sensibilisiert.
Seit Du die E-Mail verschickt hast, gehe ich damit „schwanger“, ob ich ein vielleicht „heißes Eisen“ anfassen soll.
In den angehängten Informationen (des Roten Kreuzes) steht, dass das gespendete Blut auf bestimmte „Verunreinigungen“ durch Vorerkrankungen untersucht wird. Was nicht aufgeführt ist, ist eine Untersuchung, von der ich noch nicht einmal weiß, ob sie überhaupt schon durchgeführt wurde, und wenn ja, zu welchem Ergebnis sie gekommen ist, ob das gespendete Blut auch mit Substanzen der Corona-Gen-Behandlung verunreinigt sein kann. Leider zeigen ja die aktuellen Erkenntnisse, dass das Spike-Protein noch nach Jahren aktiv sein kann. Auch in gespendetem Blut? Die konkrete Frage wäre, ob das Rote Kreuz definitiv ausschließen kann, dass das nicht der Fall ist, damit ein möglicher Schaden nicht die Gefahr läuft, größer zu sein, als der Nutzen.
Soweit ich weiß, hat das Rote Kreuz bis heute keine separaten Blutbanken von „geimpftem“ und „ungeimpftem“ Blut angelegt. Wenn zu 100% ausgeschlossen werden kann, dass keine schädlichen Substanzen der Gen-Behandlung in die Blutkonserve gelangen, wäre das ja natürlich nicht nötig. Ist das so? Wenn ja, wo ist der Nachweis dazu zu finden, wie ist der aktuelle Erkenntnisstand, von wem wurden Studien dazu erarbeitet, wer hat das finanziert?
Mindestens 20% der Bevölkerung, das sind rund 16 Millionen Menschen, haben auf die Gen-Behandlung verzichtet und wollen im Ernstfall kein kontaminiertes Blut empfangen. Wie kann das Rote Kreuz belegbar und glaubhaft nachweisen, dass möglicherweise verunreinigtes Blut nicht doch in die Blutkonserven gelangt, weil sonst die Gefahr besteht, dass im Ernstfall Impfverzichter einen Schaden davontragen könnten?
Ich finde das eine wichtige Frage dem Roten Kreuz gegenüber und vielleicht wäre es auch gut, die möglichen Spender im Vorfeld für dieses heikle Thema zu sensibilisieren. Ich finde es auffällig, dass das Rote Kreuz sich hierzu weder in die eine, noch andere Richtung in den Informationen äußert, obwohl sie uns alle betrifft.
Ich schreibe diese Email aus kollegialen Gründen, aber auch zur Sensibilisierung gegenüber der Verantwortung aller Menschen gegenüber ihren Mitmenschen, die (hoffentlich nie) in die Situation kommen, einmal auf eine Blutspende angewiesen zu sein.
Wenn sich etwas Neues auf meine Nachfrage an Dich ergibt, wäre es klasse, ich würde davon erfahren.
Vielen Dank und viele Grüße
YYYYYYY
(Die Intension war, sich so vorsichtig wie möglich, quasi auf „Samtpfötchen“, an den Kern heranzupirschen. Dass es bereits Erkenntnisse dazu gibt, dass das Blut kontaminiert sein kann, wurde bewusst weggelassen, um keine Angriffsfläche zu bieten, ein „Verschwörungstheoretiker“ zu sein. Wenn die andere Seite auf einen Austausch eingestiegen wäre, wäre eine Quelle zu dieser Aussage vorhanden gewesen.)
Die Antwort:
Hallo YYYYYYY,
danke für die ausführliche Nachricht und dass du dir Gedanken zu dem Thema machst. Ich finde, man sollte Blutspenden als eine persönliche und private Sache betrachten.
Jeder und jede sollte für sich selbst abwägen, ob und unter welchen Bedingungen er oder sie das tun möchte.
Die Fragen, die du gestellt hast, sind echt speziell. Da geht's um medizinische und wissenschaftliche Themen, da kann ich als Privatperson nicht mitreden. Ich denke, dass sich Interessierte bei solchen Themen am besten direkt an medizinische Fachstellen oder das Rote Kreuz vor Ort wenden sollten, um fundierte und belastbare Informationen zu erhalten.
Mir persönlich ist es wichtig, Menschen auf die Möglichkeit der Blutspende aufmerksam zu machen.
Jeder kann das für sich selbst entscheiden und es ist auch okay, wenn man dabei Überzeugungen hat.
Beste Grüße
XXXXXXX
(„Blutspende…eine persönliche und private Sache“, nach dem Corona-Ereignis auch noch?, „…ich als Privatperson“ empfehle anderen etwas, bei dem sie möglicherweise anderen einen Schaden zufügen. Ist das schon grob fahrlässig, nach den Denkanstößen, die gegeben wurden?, „Wenn man dabei Überzeugungen hat.“, interessante Formulierung.)
Darauf die Reaktion:
Hallo XXXXXXX,
danke auch für Deine Antwort.
Wenn so eine im Grundsatz sicher gute Aktion beworben wird, liegt es nach meinem Empfinden auch in der Verantwortung, auf mögliche Folgen hinzuweisen, wenn es das Rote Kreuz schon nicht tut. Vorausgesetzt, man misst ihnen Bedeutung zu. Wenn meine E-Mail keine Veranlassung zu einer Beunruhigung und eigener Recherche angeregt hat, dann kann ich leider mehr nicht tun.
Dass das Rote Kreuz keine Hinweise gibt, liegt wohl daran, dass es Teil des Systems ist. Wer die Augen aufmacht, kann mit wenig Aufwand leider mehr als genug Tatsachenwahrheiten finden, die mit Schäden im Zusammenhang der Gen-Behandlung verursacht wurden und immer noch verursacht werden. Es ist nicht meine Aufgabe, einen Wissensrückstand von 5 Jahren auf den aktuellen Stand zu bringen. Allein die veröffentlichten RKI-Protokolle sollten schon genug Anlass zur Skepsis bieten. Der ÖRR berichtet leider nicht darüber, weil er auch Teil des Systems ist.
Ich will es damit genug sein lassen und hoffe, dass es unter den Kolleginnen und Kollegen noch weitere kritische Geister gibt.
Es geht nicht gegen Dich persönlich, aber ich hoffe, das Angebot wird nicht zahlreich genutzt.
Viele Grüße
YYYYYYY
(Einen halben Gang hochgeschaltet, ein Versuch, XXXXXXX aus der Reserve zu locken.)
Und ein Nachtrag von YYYYYYY:
Lieber XXXXXXX,
wir sind schon einmal unter Missbrauch des Begriffes „Solidarität“ hinter die Fichte geführt worden. Das darf nicht noch einmal passieren!
Nochmals viele Grüße
YYYYYYY
(Keine Reaktion mehr von XXXXXXX)
Und, wie gesagt, daraufhin kam das Video mit Bonhoeffer entgegen. Besser kann man vorsätzliche, rationale Ignoranz in Bezug auf den Schriftwechsel nicht beschreiben.
Hier wird eine jeden angehende allgemeinmedizinische Frage zu einer Frage der persönlichen Überzeugung gemacht. Das kommt doch sehr bekannt vor, oder?
Sehr wahrscheinlich lässt es sich vermuten, dass es sich bei XXXXXXX wohl um einen Corona-Jünger handelt, der die Tatsachen scheut, wie der Teufel das Weihwasser. Bloß nicht nachdenken, bloß nicht in Frage stellen, bloß nicht hellhörig oder gar neugierig werden, bloß nicht auf die Äußerungen eingehen, bloß nicht konkret werden, bloß keine eindeutig formulierte Stellung zu den Aussagen beziehen. „Angriffsfläche“ wäre vorhanden gewesen.
Das vorsichtige Anpirschen war alles andere, als mit-der-Brechstange-herangehen. Und doch setzt sofort automatisch der Teflon-Effekt ein. Selbstschutz.
Die Frage ist, wie soll da die Spaltung überwunden werden, wenn „die andere Seite“ so überhaupt nicht bereit ist, sich mit dem Vorgebrachten auseinanderzusetzen. Noch nicht einmal, wenn man nur die Spitze der Spitze des Eisbergs leise anhaucht.
Diesem Beispiel könnten viele unzählige weitere Beispiele hinzugefügt werden. Jeder hat so etwas schon einmal auf die eine oder andere Weise erlebt.
Das Gefühl lässt sich nicht unterdrücken, dass sich die Menschheit in zwei Lager aufgeteilt hat, und es gibt derzeit keinen Weg, wie man wieder aufeinander zukommen könnte.
Wie zwei Welten aufeinanderprallen, kann man derzeit auch in der Enquete-Kommission im sächsischen Landtag erleben: https://www.youtube.com/watch?v=D6ACmwBUBFM
Aus der Sicht von YYYYYYY ist das kein Grund zur Verzweiflung, jedoch drängt sich der Wunsch auf, dass man mit solchen Menschen wie XXXXXXX nichts mehr anfangen will. Man möchte mit ihnen, so schade es auch ist, am liebsten gar nichts mehr zu tun haben, und wenn doch aus irgendwelchen Gründen, nur noch das Allernotwendigste, so kurz und knapp, wie möglich. Empathie aufzubringen erscheint einem als vergeudete Energie, besser ist es, sich auf die Menschen zu konzentrieren, die wegen fehlender Genbehandlung keine Wesensveränderungen, die mittlerweile leider auch schon bestätigt sind, erlitten haben.
Wie Bonhoeffer richtig sagt, es geht hier nicht um Intelligenz, es geht viel tiefer. Es geht um das Menschsein an sich, und man hat den Eindruck, dass vor allem dies unter dem Einfluss der Spritze sehr stark gelitten hat. Da scheint so eine Abgestumpftheit durch, die einem einen kalten Schauer über den Rücken fahren lässt. Und das ist vielleicht noch gefährlicher, als diejenigen, die wirklich dumm sind. Das ist keine Arroganz oder Überheblichkeit, sondern unschuldig, wahllos von der Natur vergebene Dummheit, die jeden hätte ereilen können, hat es immer schon zu einem großen Teil gegeben. Hier hat man wenigstens noch die Möglichkeit, sich einfühlen zu können und Verständnis aufzubringen. Bei Menschen aber, von denen man weiß, dass sie die kognitiven Fähigkeiten zur Reflektion hätten, sie jedoch aus welchen Gründen auch immer nicht nutzen, oder sie als Verdrängungsmechanismus gerade nutzen, weil sie es können, geht auch eine gewisse Gefahr aus, weil man nie wissen kann, was sie sich sonst noch so ausdenken könnten, wenn sie in die geistige Enge getrieben werden, um ja nicht von Menschen, die den Mut haben, die Wahrheit auszusprechen, in ihrem mühsam aufgebauten Weltbild erschüttert zu werden. „Was nicht sein darf, das nicht sein kann!“, obwohl doch eigentlich die Wahrheit dem Menschen zumutbar ist.
So hat man das Gefühl, man atmet Honig ein und bewegt sich mühsam durch einen zähen Brei vorwärts, der einem bis zu den Oberschenkeln reicht. Jeder Schritt eine Anstrengung.
Und bevor man noch tiefer in dieses Verlustgefühl von Lebensqualität eintaucht (das hat nichts mit Depressionen zu tun, man bekommt einfach nur schlechte Laune), sich immer wieder bewusst machen, dass es da draußen noch eine Menge bei Verstand gebliebener Menschen gibt, die unermüdlich daran arbeiten, dass die Wahrheit weiter so sehr erkraftet, dass sie sich ihren Weg in den sogenannten Mainstream bahnt und die Menschen endlich aufwachen. So schmerzlich das für viele sein mag, es muss sein!
Selbst für einen wenig religiösen Menschen, im Sinne von regelmäßigen Kirchgängen und keinem Kontakt zur Institution Kirche, bekommt der Satz eine ganz besondere Bedeutung:
„Ich schicke euch den Geist der Wahrheit, und der wird euch frei machen!“
-
 @ 0fa80bd3:ea7325de
2025-02-14 23:24:37
@ 0fa80bd3:ea7325de
2025-02-14 23:24:37intro
The Russian state made me a Bitcoiner. In 1991, it devalued my grandmother's hard-earned savings. She worked tirelessly in the kitchen of a dining car on the Moscow–Warsaw route. Everything she had saved for my sister and me to attend university vanished overnight. This story is similar to what many experienced, including Wences Casares. The pain and injustice of that time became my first lessons about the fragility of systems and the value of genuine, incorruptible assets, forever changing my perception of money and my trust in government promises.
In 2014, I was living in Moscow, running a trading business, and frequently traveling to China. One day, I learned about the Cypriot banking crisis and the possibility of moving money through some strange thing called Bitcoin. At the time, I didn’t give it much thought. Returning to the idea six months later, as a business-oriented geek, I eagerly began studying the topic and soon dove into it seriously.
I spent half a year reading articles on a local online journal, BitNovosti, actively participating in discussions, and eventually joined the editorial team as a translator. That’s how I learned about whitepapers, decentralization, mining, cryptographic keys, and colored coins. About Satoshi Nakamoto, Silk Road, Mt. Gox, and BitcoinTalk. Over time, I befriended the journal’s owner and, leveraging my management experience, later became an editor. I was drawn to the crypto-anarchist stance and commitment to decentralization principles. We wrote about the economic, historical, and social preconditions for Bitcoin’s emergence, and it was during this time that I fully embraced the idea.
It got to the point where I sold my apartment and, during the market's downturn, bought 50 bitcoins, just after the peak price of $1,200 per coin. That marked the beginning of my first crypto winter. As an editor, I organized workflows, managed translators, developed a YouTube channel, and attended conferences in Russia and Ukraine. That’s how I learned about Wences Casares and even wrote a piece about him. I also met Mikhail Chobanyan (Ukrainian exchange Kuna), Alexander Ivanov (Waves project), Konstantin Lomashuk (Lido project), and, of course, Vitalik Buterin. It was a time of complete immersion, 24/7, and boundless hope.
After moving to the United States, I expected the industry to grow rapidly, attended events, but the introduction of BitLicense froze the industry for eight years. By 2017, it became clear that the industry was shifting toward gambling and creating tokens for the sake of tokens. I dismissed this idea as unsustainable. Then came a new crypto spring with the hype around beautiful NFTs – CryptoPunks and apes.
I made another attempt – we worked on a series called Digital Nomad Country Club, aimed at creating a global project. The proceeds from selling images were intended to fund the development of business tools for people worldwide. However, internal disagreements within the team prevented us from completing the project.
With Trump’s arrival in 2025, hope was reignited. I decided that it was time to create a project that society desperately needed. As someone passionate about history, I understood that destroying what exists was not the solution, but leaving everything as it was also felt unacceptable. You can’t destroy the system, as the fiery crypto-anarchist voices claimed.
With an analytical mindset (IQ 130) and a deep understanding of the freest societies, I realized what was missing—not only in Russia or the United States but globally—a Bitcoin-native system for tracking debts and financial interactions. This could return control of money to ordinary people and create horizontal connections parallel to state systems. My goal was to create, if not a Bitcoin killer app, then at least to lay its foundation.
At the inauguration event in New York, I rediscovered the Nostr project. I realized it was not only technologically simple and already quite popular but also perfectly aligned with my vision. For the past month and a half, using insights and experience gained since 2014, I’ve been working full-time on this project.
-
 @ 5c26ee8b:a4d229aa
2025-06-04 21:29:51
@ 5c26ee8b:a4d229aa
2025-06-04 21:29:51Since late December, 2024, an evil magic attack targeted me and my family as well as many people occupying governmental positions. The attack was involving the Antichrist that was on an unreachable island found by me telepathically. Sadly the information about the Antichrist reached some Russian Oligarchs Among which many Jews. And somehow he was contacted by them as well as many other Antichrist Allies among which Royal families and he led the magic attack even though magic mixed with AI and computer technologies. The attack consisted in whispering of the devils, of mankind (Antichrist allies) and jinns. Physical harm was attempted too although so weak for any significant effect for me at least. I hesitated on killing the Antichrist because his appearance is a sign of Judgement Day, however, because of acknowledging that the attack would be too intense for ordinary people that don’t know how to know the difference between inner voice or whispering of the devils I have decided to kill him by requesting that he is burned in the core of the earth and by turning any remains into dust spread in space. He didn’t have only a physical presence though he had an incorporated devil. So it took a while to kill the devil that was isolated in iron coffin first so it assumed a smaller figure while trying to escape and finally God guided me to request that the devil is hit with fireballs over and over again. It was confirmed to me that the devil of the Antichrist was completely burned out. And that the next sign would be the creature coming out of the earth, Ad-Daba as well as the smoke covering all the earth, with which there is a great punishment, and that I would be able to fly too (good for me). I hesitated on spreading the news about the Antichrist to avoid fitnah (confusion and trial). Also because he was never freed out of the island before getting burned out. I am mentioning this because it’s important to know that when God’s punishment comes and when the great signs of Judgement Day (among which what’s mentioned above) would appear the returning to God in belief or in repentance won’t be accepted; so my advise is to do it now.
27:82 An-Naml
۞ وَإِذَا وَقَعَ الْقَوْلُ عَلَيْهِمْ أَخْرَجْنَا لَهُمْ دَابَّةً مِنَ الْأَرْضِ تُكَلِّمُهُمْ أَنَّ النَّاسَ كَانُوا بِآيَاتِنَا لَا يُوقِنُونَ
And when the word befalls them, We will bring forth for them a creature from the earth speaking to them, [saying] that the people were, of Our verses, not certain [in faith].
- Ad-Dukhaan
حم
Ha, Meem.
وَالْكِتَابِ الْمُبِينِ
By the clear Book,
إِنَّا أَنْزَلْنَاهُ فِي لَيْلَةٍ مُبَارَكَةٍ ۚ إِنَّا كُنَّا مُنْذِرِينَ
Indeed, We sent it down during a blessed night. Indeed, We were to warn [mankind].
فِيهَا يُفْرَقُ كُلُّ أَمْرٍ حَكِيمٍ
On that night is made distinct every precise matter -
أَمْرًا مِنْ عِنْدِنَا ۚ إِنَّا كُنَّا مُرْسِلِينَ
[Every] matter [proceeding] from Us. Indeed, We were to send [a messenger]
رَحْمَةً مِنْ رَبِّكَ ۚ إِنَّهُ هُوَ السَّمِيعُ الْعَلِيمُ
As mercy from your Lord. Indeed, He is the Hearing, the Knowing.
رَبِّ السَّمَاوَاتِ وَالْأَرْضِ وَمَا بَيْنَهُمَا ۖ إِنْ كُنْتُمْ مُوقِنِينَ
Lord of the heavens and the earth and that between them, if you would be certain.
لَا إِلَٰهَ إِلَّا هُوَ يُحْيِي وَيُمِيتُ ۖ رَبُّكُمْ وَرَبُّ آبَائِكُمُ الْأَوَّلِينَ
There is no deity except Him; He gives life and causes death. [He is] your Lord and the Lord of your first forefathers.
بَلْ هُمْ فِي شَكٍّ يَلْعَبُونَ
But they are in doubt, amusing themselves.
فَارْتَقِبْ يَوْمَ تَأْتِي السَّمَاءُ بِدُخَانٍ مُبِينٍ
Then watch for the Day when the sky will bring a visible smoke.
يَغْشَى النَّاسَ ۖ هَٰذَا عَذَابٌ أَلِيمٌ
Covering the people; this is a painful torment.
رَبَّنَا اكْشِفْ عَنَّا الْعَذَابَ إِنَّا مُؤْمِنُونَ
[They will say], "Our Lord, remove from us the torment; indeed, we are believers."
أَنَّىٰ لَهُمُ الذِّكْرَىٰ وَقَدْ جَاءَهُمْ رَسُولٌ مُبِينٌ
How will there be for them a reminder [at that time]? And there had come to them a clear Messenger.
ثُمَّ تَوَلَّوْا عَنْهُ وَقَالُوا مُعَلَّمٌ مَجْنُونٌ
Then they turned away from him and said, "[He was] taught [and is] a madman."
إِنَّا كَاشِفُو الْعَذَابِ قَلِيلًا ۚ إِنَّكُمْ عَائِدُونَ
Indeed, We will remove the torment for a little. Indeed, you [disbelievers] will return [to disbelief].
يَوْمَ نَبْطِشُ الْبَطْشَةَ الْكُبْرَىٰ إِنَّا مُنْتَقِمُونَ
The Day We will strike with the greatest assault, indeed, We will take retribution.
6:158 Al-An'aam
هَلْ يَنْظُرُونَ إِلَّا أَنْ تَأْتِيَهُمُ الْمَلَائِكَةُ أَوْ يَأْتِيَ رَبُّكَ أَوْ يَأْتِيَ بَعْضُ آيَاتِ رَبِّكَ ۗ يَوْمَ يَأْتِي بَعْضُ آيَاتِ رَبِّكَ لَا يَنْفَعُ نَفْسًا إِيمَانُهَا لَمْ تَكُنْ آمَنَتْ مِنْ قَبْلُ أَوْ كَسَبَتْ فِي إِيمَانِهَا خَيْرًا ۗ قُلِ انْتَظِرُوا إِنَّا مُنْتَظِرُونَ
Do they [then] wait for anything except that the angels should come to them or your Lord should come or that there come some of the signs of your Lord? The Day that some of the signs of your Lord will come no soul will benefit from its faith as long as it had not believed before or had earned through its faith some good. Say, "Wait. Indeed, we [also] are waiting."
4:17 An-Nisaa
إِنَّمَا التَّوْبَةُ عَلَى اللَّهِ لِلَّذِينَ يَعْمَلُونَ السُّوءَ بِجَهَالَةٍ ثُمَّ يَتُوبُونَ مِنْ قَرِيبٍ فَأُولَٰئِكَ يَتُوبُ اللَّهُ عَلَيْهِمْ ۗ وَكَانَ اللَّهُ عَلِيمًا حَكِيمًا
The repentance accepted by Allah is only for those who do wrong in ignorance [or carelessness] and then repent soon after. It is those to whom Allah will turn in forgiveness, and Allah is ever Knowing and Wise.
4:18 An-Nisaa
وَلَيْسَتِ التَّوْبَةُ لِلَّذِينَ يَعْمَلُونَ السَّيِّئَاتِ حَتَّىٰ إِذَا حَضَرَ أَحَدَهُمُ الْمَوْتُ قَالَ إِنِّي تُبْتُ الْآنَ وَلَا الَّذِينَ يَمُوتُونَ وَهُمْ كُفَّارٌ ۚ أُولَٰئِكَ أَعْتَدْنَا لَهُمْ عَذَابًا أَلِيمًا
But repentance is not [accepted] of those who [continue to] do evil deeds up until, when death comes to one of them, he says, "Indeed, I have repented now," or of those who die while they are disbelievers. For them We have prepared a painful punishment.
4:47 An-Nisaa
يَا أَيُّهَا الَّذِينَ أُوتُوا الْكِتَابَ آمِنُوا بِمَا نَزَّلْنَا مُصَدِّقًا لِمَا مَعَكُمْ مِنْ قَبْلِ أَنْ نَطْمِسَ وُجُوهًا فَنَرُدَّهَا عَلَىٰ أَدْبَارِهَا أَوْ نَلْعَنَهُمْ كَمَا لَعَنَّا أَصْحَابَ السَّبْتِ ۚ وَكَانَ أَمْرُ اللَّهِ مَفْعُولًا
O you who were given the Scripture, believe in what We have sent down [to Muhammad], confirming that which is with you, before We obliterate faces and turn them toward their backs or curse them as We cursed the sabbath-breakers. And ever is the decree of Allah accomplished.
4:48 An-Nisaa
إِنَّ اللَّهَ لَا يَغْفِرُ أَنْ يُشْرَكَ بِهِ وَيَغْفِرُ مَا دُونَ ذَٰلِكَ لِمَنْ يَشَاءُ ۚ وَمَنْ يُشْرِكْ بِاللَّهِ فَقَدِ افْتَرَىٰ إِثْمًا عَظِيمًا
Indeed, Allah does not forgive association with Him, but He forgives what is less than that for whom He wills. And he who associates others with Allah has certainly fabricated a tremendous sin.
41:13 Fussilat
فَإِنْ أَعْرَضُوا فَقُلْ أَنْذَرْتُكُمْ صَاعِقَةً مِثْلَ صَاعِقَةِ عَادٍ وَثَمُودَ
But if they turn away, then say, "I have warned you of a thunderbolt like the thunderbolt [that struck] 'Aad and Thamud.
61:13 As-Saff
وَأُخْرَىٰ تُحِبُّونَهَا ۖ نَصْرٌ مِنَ اللَّهِ وَفَتْحٌ قَرِيبٌ ۗ وَبَشِّرِ الْمُؤْمِنِينَ
And [you will obtain] another [favor] that you love - victory from Allah and an imminent conquest; and give good tidings to the believers.
-
 @ 45ea632c:bb0b4fa1
2025-06-05 08:01:04
@ 45ea632c:bb0b4fa1
2025-06-05 08:01:04No mundo do entretenimento digital, a inovação e a experiência do usuário são fatores determinantes para o sucesso de uma plataforma. A Win44 surge como uma das opções mais promissoras do mercado brasileiro, oferecendo uma experiência completa e diferenciada para quem busca diversão, praticidade e oportunidades de ganhos reais. Com uma interface moderna, variedade de jogos e suporte de alta qualidade, a Win44 tem se destacado entre as preferidas dos jogadores.
Uma Plataforma Moderna e Intuitiva Desde o primeiro acesso, a Win44 impressiona pelo seu design moderno, navegação fluida e compatibilidade com diferentes dispositivos. Seja no computador, tablet ou smartphone, a plataforma se adapta perfeitamente, garantindo uma experiência sem interrupções e totalmente otimizada.
Além da estética, a funcionalidade também chama atenção. Os menus são organizados de forma clara, facilitando a busca por jogos, promoções e informações da conta do usuário. Isso é ideal tanto para iniciantes quanto para jogadores mais experientes, que valorizam a praticidade no dia a dia.
Variedade de Jogos para Todos os Perfis Um dos grandes diferenciais da win44é a sua biblioteca de jogos, que abrange diferentes gostos e estilos. A plataforma conta com opções que vão desde os clássicos de mesa até os jogos de azar mais populares, todos desenvolvidos por fornecedores renomados da indústria.
Entre os destaques, estão os jogos de cartas como pôquer, bacará e blackjack, além de uma ampla seleção de jogos de roleta e máquinas de giros com diferentes temáticas e dinâmicas. Os gráficos são envolventes, com animações fluidas e efeitos sonoros que aumentam a imersão do jogador, proporcionando uma experiência realista e empolgante.
Outro ponto positivo é a presença de jogos ao vivo com crupiês reais, o que adiciona uma camada extra de emoção e interação, aproximando ainda mais o jogador da atmosfera dos grandes centros de entretenimento internacionais.
Experiência do Jogador em Primeiro Lugar A Win44 investe constantemente na qualidade do atendimento ao usuário e na segurança da plataforma. O suporte está disponível 24 horas por dia, todos os dias da semana, com atendimento em português e canais de fácil acesso, como chat ao vivo e e-mail.
No quesito segurança, a plataforma utiliza tecnologia de criptografia avançada para proteger todas as transações e dados dos usuários, garantindo total confidencialidade. Além disso, o processo de registro é simples e rápido, permitindo que o jogador comece a se divertir em poucos minutos.
Outro ponto muito valorizado pelos usuários é a variedade de métodos de pagamento e saque. A Win44 oferece suporte a diversas opções, incluindo transferências bancárias, carteiras digitais e até pagamentos via PIX, que têm ganhado grande popularidade no Brasil por sua rapidez e conveniência.
Bônus e Promoções Atrativas Para tornar a experiência ainda mais interessante, a Win44 oferece uma gama de promoções e bônus regulares. Novos usuários podem aproveitar ofertas de boas-vindas que aumentam o saldo inicial, enquanto jogadores frequentes têm acesso a promoções sazonais, sorteios e programas de fidelidade.
Essas vantagens não apenas elevam o nível da diversão, mas também aumentam as chances de obter bons resultados durante as partidas.
Conclusão A Win44 é uma plataforma completa que combina tecnologia, diversidade e um atendimento de excelência para proporcionar a melhor experiência de entretenimento online. Com um ambiente seguro, jogos variados e uma interface amigável, ela se consolida como uma das principais escolhas para jogadores brasileiros que buscam diversão de qualidade.
-
 @ 472f440f:5669301e
2025-06-04 20:58:53
@ 472f440f:5669301e
2025-06-04 20:58:53Marty's Bent
J.P. Morgan CEO Jamie Dimon has long been an outspoken skeptic and critic of bitcoin. He has called Bitcoin a speculative asset, a fraud, a pet rock, and has opined that it will inevitably blow up. A couple of years ago, he was on Capitol Hill saying that if he were the government, he would "close it down". Just within the last month, he was on Fox Business News talking with Maria Bartiromo, proclaiming that the U.S. should be stockpiling bullets and rare earth metals instead of bitcoin. It's pretty clear that Jamie Dimon, who is at the helm of the most powerful and largest bank in the world, does not like bitcoin one bit.
Evidence below:

via Bitcoin Magazine

via me
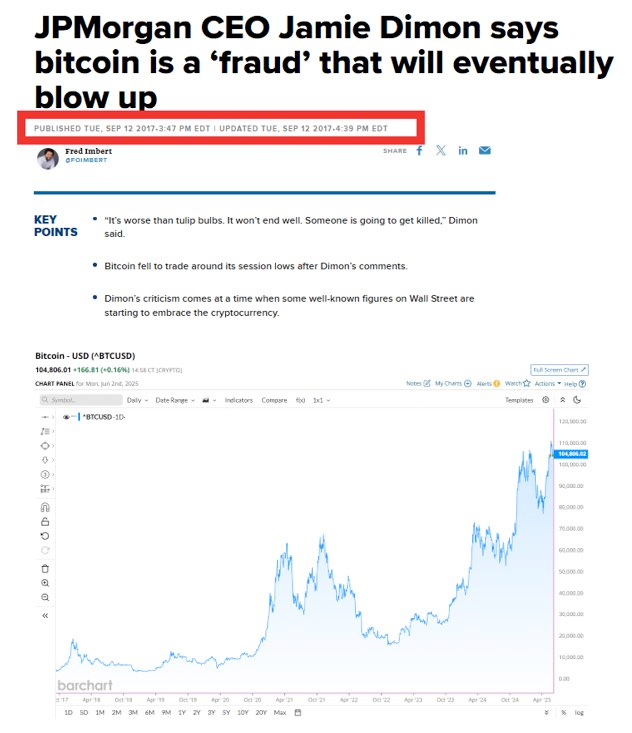
via CNBC

Despite Dimon's distinguished disdain for Bitcoin, J.P. Morgan cannot deny reality. The CEO of the largest bank in the world is certainly a powerful man, but no one individual, even in the position that Jamie Dimon is in, is more powerful than the market. And the market has spoken very clearly, it is demanding bitcoin. The Bitcoin ETFs have been the most successful ETFs in terms of pace of growth since their launch. They've accumulated tens of billions of dollars in AUM in a very short period of time. Outpacing the previous record set by the gold ETF, GLD.
Whether or not Jamie Dimon himself likes Bitcoin doesn't matter. J.P. Morgan, as the largest bank in the world and a publicly traded company, has a duty to shareholders. And that duty is to increase shareholder value by any ethical and legal means necessary. Earlier today, J.P. Morgan announced plans to offer clients financing against their Bitcoin ETFs, as well as some other benefits, including having their bitcoin holdings recognized in their overall net worth and liquid assets, similar to stocks, cars, and art, which will be massive for bitcoiners looking to get mortgages and other types of loans.

via Bloomberg
I've talked about this recently, but trying to buy a house when most of your liquid net worth is held in bitcoin is a massive pain in the ass. Up until this point, if you wanted to have your bitcoin recognized as part of your net worth and count towards your overall credit profile, you would need to sell some bitcoin, move it to a bank account, and have it sit there for a certain period of time before it was recognized toward your net worth. This is not ideal for bitcoiners who have sufficient cash flows and don't want to sell their bitcoin, pay the capital gains tax, and risk not being able to buy back the amount of sats they were forced to sell just to get a mortgage.
It's not yet clear to me whether or not J.P. Morgan will recognize bitcoin in cold storage toward their clients' net worth and credit profile, or if this is simply for bitcoin ETFs only. However, regardless, this is a step in the right direction and a validation of something that many bitcoiners have been saying for years. Inevitably, everyone will have to bend the knee to bitcoin. Today, it just happened to be the largest bank in the world. I expect more of this to come in the coming months, years, and decades.
Lyn Alden likes to say it in the context of the U.S. national debt and the fiscal crisis, but it also applies to bitcoin adoption and the need for incumbents to orient themselves around the demands of individual bitcoiners; nothing stops this train.
Corporate Bitcoin Treasuries are Changing Market Dynamics
Leon Wankum revealed how corporate Bitcoin treasuries are fundamentally reshaping business dynamics. Companies can now issue equity to fund operations while preserving their Bitcoin holdings, creating a revolutionary capital structure. Leon highlighted MicroStrategy's position, noting they hold enough Bitcoin to cover dividend payments for over 200 years. This model enables companies to reduce founder dilution since they don't need repeated funding rounds when their treasury appreciates.
"Some companies' Bitcoin treasuries are now worth more than all money they've ever raised." - Leon Wankum
Leon shared examples from his own portfolio companies where this strategy has proven transformative. Public companies have discovered an entirely new business model through strategic dilution that actually increases BTC per share. As Leon explained, this approach allows firms to leverage equity markets for operational funding while their Bitcoin treasury compounds in value, creating a positive feedback loop that benefits both shareholders and the company's long-term sustainability.
Check out the full podcast here for more on real estate price cycles, Bitcoin lending products, and the transition to a Bitcoin standard.
Headlines of the Day
California May Seize Idle Bitcoin After 3 Years - via X
Semler Scientific Buys $20M More Bitcoin, Holds $467M - via X
US Home Sellers Surge as Buyers Hit 4-Year Low - via X
Get our new STACK SATS hat - via tftcmerch.io
Take the First Step Off the Exchange
Bitkey is an easy, secure way to move your Bitcoin into self-custody. With simple setup and built-in recovery, it’s the perfect starting point for getting your coins off centralized platforms and into cold storage—no complexity, no middlemen.
Take control. Start with Bitkey.
Use the promo code “TFTC20” during checkout for 20% off
Ten31, the largest bitcoin-focused investor, has deployed $150.00M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/invest.
Final thought...
I feel old.
Get this newsletter sent to your inbox daily: https://www.tftc.io/bitcoin-brief/
Subscribe to our YouTube channels and follow us on Nostr and X:
-
 @ daa41bed:88f54153
2025-02-09 16:50:04
@ daa41bed:88f54153
2025-02-09 16:50:04There has been a good bit of discussion on Nostr over the past few days about the merits of zaps as a method of engaging with notes, so after writing a rather lengthy article on the pros of a strategic Bitcoin reserve, I wanted to take some time to chime in on the much more fun topic of digital engagement.
Let's begin by defining a couple of things:
Nostr is a decentralized, censorship-resistance protocol whose current biggest use case is social media (think Twitter/X). Instead of relying on company servers, it relies on relays that anyone can spin up and own their own content. Its use cases are much bigger, though, and this article is hosted on my own relay, using my own Nostr relay as an example.
Zap is a tip or donation denominated in sats (small units of Bitcoin) sent from one user to another. This is generally done directly over the Lightning Network but is increasingly using Cashu tokens. For the sake of this discussion, how you transmit/receive zaps will be irrelevant, so don't worry if you don't know what Lightning or Cashu are.
If we look at how users engage with posts and follows/followers on platforms like Twitter, Facebook, etc., it becomes evident that traditional social media thrives on engagement farming. The more outrageous a post, the more likely it will get a reaction. We see a version of this on more visual social platforms like YouTube and TikTok that use carefully crafted thumbnail images to grab the user's attention to click the video. If you'd like to dive deep into the psychology and science behind social media engagement, let me know, and I'd be happy to follow up with another article.
In this user engagement model, a user is given the option to comment or like the original post, or share it among their followers to increase its signal. They receive no value from engaging with the content aside from the dopamine hit of the original experience or having their comment liked back by whatever influencer they provide value to. Ad revenue flows to the content creator. Clout flows to the content creator. Sales revenue from merch and content placement flows to the content creator. We call this a linear economy -- the idea that resources get created, used up, then thrown away. Users create content and farm as much engagement as possible, then the content is forgotten within a few hours as they move on to the next piece of content to be farmed.
What if there were a simple way to give value back to those who engage with your content? By implementing some value-for-value model -- a circular economy. Enter zaps.

Unlike traditional social media platforms, Nostr does not actively use algorithms to determine what content is popular, nor does it push content created for active user engagement to the top of a user's timeline. Yes, there are "trending" and "most zapped" timelines that users can choose to use as their default, but these use relatively straightforward engagement metrics to rank posts for these timelines.
That is not to say that we may not see clients actively seeking to refine timeline algorithms for specific metrics. Still, the beauty of having an open protocol with media that is controlled solely by its users is that users who begin to see their timeline gamed towards specific algorithms can choose to move to another client, and for those who are more tech-savvy, they can opt to run their own relays or create their own clients with personalized algorithms and web of trust scoring systems.
Zaps enable the means to create a new type of social media economy in which creators can earn for creating content and users can earn by actively engaging with it. Like and reposting content is relatively frictionless and costs nothing but a simple button tap. Zaps provide active engagement because they signal to your followers and those of the content creator that this post has genuine value, quite literally in the form of money—sats.

I have seen some comments on Nostr claiming that removing likes and reactions is for wealthy people who can afford to send zaps and that the majority of people in the US and around the world do not have the time or money to zap because they have better things to spend their money like feeding their families and paying their bills. While at face value, these may seem like valid arguments, they, unfortunately, represent the brainwashed, defeatist attitude that our current economic (and, by extension, social media) systems aim to instill in all of us to continue extracting value from our lives.
Imagine now, if those people dedicating their own time (time = money) to mine pity points on social media would instead spend that time with genuine value creation by posting content that is meaningful to cultural discussions. Imagine if, instead of complaining that their posts get no zaps and going on a tirade about how much of a victim they are, they would empower themselves to take control of their content and give value back to the world; where would that leave us? How much value could be created on a nascent platform such as Nostr, and how quickly could it overtake other platforms?
Other users argue about user experience and that additional friction (i.e., zaps) leads to lower engagement, as proven by decades of studies on user interaction. While the added friction may turn some users away, does that necessarily provide less value? I argue quite the opposite. You haven't made a few sats from zaps with your content? Can't afford to send some sats to a wallet for zapping? How about using the most excellent available resource and spending 10 seconds of your time to leave a comment? Likes and reactions are valueless transactions. Social media's real value derives from providing monetary compensation and actively engaging in a conversation with posts you find interesting or thought-provoking. Remember when humans thrived on conversation and discussion for entertainment instead of simply being an onlooker of someone else's life?
If you've made it this far, my only request is this: try only zapping and commenting as a method of engagement for two weeks. Sure, you may end up liking a post here and there, but be more mindful of how you interact with the world and break yourself from blind instinct. You'll thank me later.

-
 @ e3ba5e1a:5e433365
2025-02-05 17:47:16
@ e3ba5e1a:5e433365
2025-02-05 17:47:16I got into a friendly discussion on X regarding health insurance. The specific question was how to deal with health insurance companies (presumably unfairly) denying claims? My answer, as usual: get government out of it!
The US healthcare system is essentially the worst of both worlds:
- Unlike full single payer, individuals incur high costs
- Unlike a true free market, regulation causes increases in costs and decreases competition among insurers
I'm firmly on the side of moving towards the free market. (And I say that as someone living under a single payer system now.) Here's what I would do:
- Get rid of tax incentives that make health insurance tied to your employer, giving individuals back proper freedom of choice.
- Reduce regulations significantly.
-
In the short term, some people will still get rejected claims and other obnoxious behavior from insurance companies. We address that in two ways:
- Due to reduced regulations, new insurance companies will be able to enter the market offering more reliable coverage and better rates, and people will flock to them because they have the freedom to make their own choices.
- Sue the asses off of companies that reject claims unfairly. And ideally, as one of the few legitimate roles of government in all this, institute new laws that limit the ability of fine print to allow insurers to escape their responsibilities. (I'm hesitant that the latter will happen due to the incestuous relationship between Congress/regulators and insurers, but I can hope.)
Will this magically fix everything overnight like politicians normally promise? No. But it will allow the market to return to a healthy state. And I don't think it will take long (order of magnitude: 5-10 years) for it to come together, but that's just speculation.
And since there's a high correlation between those who believe government can fix problems by taking more control and demanding that only credentialed experts weigh in on a topic (both points I strongly disagree with BTW): I'm a trained actuary and worked in the insurance industry, and have directly seen how government regulation reduces competition, raises prices, and harms consumers.
And my final point: I don't think any prior art would be a good comparison for deregulation in the US, it's such a different market than any other country in the world for so many reasons that lessons wouldn't really translate. Nonetheless, I asked Grok for some empirical data on this, and at best the results of deregulation could be called "mixed," but likely more accurately "uncertain, confused, and subject to whatever interpretation anyone wants to apply."
https://x.com/i/grok/share/Zc8yOdrN8lS275hXJ92uwq98M
-
 @ e516ecb8:1be0b167
2025-06-04 20:33:38
@ e516ecb8:1be0b167
2025-06-04 20:33:38Imagina un mundo donde cada peso que gastas es vigilado, registrado y cuestionado. Donde el Estado decide si puedes comprar un café, una manzana o una criptomoneda. No es una distopía de ciencia ficción, es el rumbo que están tomando varios países, mientras otros, como Argentina, dan un giro inesperado hacia la libertad. ¿Quién está ganando esta batalla por el control de tu dinero?
Argentina: "Tus dólares son tuyos" En Argentina, Javier Milei, con su bandera libertaria ondeando, ha dado un paso audaz: desmantelar el control policial sobre el dinero de los ciudadanos. Su lema, "Tus dólares son tuyos", es tan obvio como revolucionario. Después de décadas de corralitos, cepos cambiarios y una inflación que en 2023 alcanzó el 211,4% según el INDEC, Milei apuesta por devolverle al ciudadano el poder sobre su propio capital. Con el país logrando superávit fiscal por primera vez en años (0,2% del PBI en el primer trimestre de 2024), el gobierno ya no necesita espiar cada transacción para exprimir impuestos.
Pero aquí viene lo curioso: encuestas recientes, como una de la consultora Poliarquía, muestran que un 35% de los argentinos aún prefiere que el Estado controle sus finanzas. ¿Masoquismo? ¿Miedo a la libertad? Tal vez sea la costumbre de vivir bajo la lupa. Milei, fiel a su convicción, no solo liberaliza por necesidad económica, sino porque cree que el dinero es tuyo, no del burócrata de turno.
España y el Euro Digital: El ojo que todo lo ve Mientras Argentina afloja las riendas, Europa cabalga en dirección opuesta. En España, el gobierno está reduciendo progresivamente los umbrales para controlar transacciones bancarias. A partir de 2026, cada pago por Bizum —el equivalente ibérico al Pix brasileño— estará bajo escrutinio. Según el Banco de España, en 2024 se realizaron más de 1.200 millones de transacciones por Bizum, moviendo unos 60.000 millones de euros. Ahora, cada una de esas operaciones será un dato más para Hacienda.
Pero no es solo España. La Unión Europea avanza con el Euro Digital, un proyecto que promete ser la pesadilla de cualquier amante de la privacidad. Esta moneda digital, según el Banco Central Europeo, permitirá rastrear cada movimiento, limitar ciertos gastos (¿adiós a compras de cripto o donaciones incómodas?), e incluso programar que el dinero "se oxide". Sí, has leído bien: si no gastas tus euros digitales en un tiempo determinado, podrían perder valor o simplemente desaparecer. Un informe del BCE de 2023 estima que el Euro Digital estará operativo en 2027, y ya hay pruebas piloto en países como Alemania y Francia. ¿Libertad financiera? Más bien un Gran Hermano con esteroides.
Chile: El Estado fisgón y los funcionarios de lujo En Chile, el control monetario también aprieta. El gobierno ha propuesto levantar el secreto bancario, permitiendo que cualquier funcionario del SII pueda husmear en tus cuentas. Además, si haces más de 50 transacciones al mes, el Servicio de Impuestos Internos (SII) pondrá la lupa sobre ti. ¿Y las ferias libres? Esas donde compras tus tomates y zapallos sin complicaciones ahora deberán emitir boletas electrónicas, encareciendo los productos para el ciudadano de a pie. Según la CEPAL, los costos administrativos para pequeños comerciantes podrían aumentar hasta un 15% con estas medidas.
Mientras tanto, el sector público chileno vive en otra galaxia. Funcionarios con sueldos que superan los 5 millones de pesos mensuales (unos 5.500 USD) toman licencias médicas para viajar por el mundo, según denuncias de la Contraloría. Algunos incluso cobran por "turnos" de 17 horas extras diarias o marcan asistencia en dos lugares al mismo tiempo. ¿Y quién paga? Tú, con tus impuestos.
La resistencia: Volver al efectivo o abrazar las cripto Si el Estado quiere controlar cada centavo, ¿qué opciones nos quedan? Una es volver al efectivo, pero no nos engañemos: el dinero fiat, controlado por bancos centrales, pierde valor a largo plazo. En Chile, la inflación acumulada entre 2010 y 2024 fue del 62%, según el INE. Tus billetes de hoy valen menos que los de ayer, y mañana valdrán aún menos.
La otra opción es el mundo cripto, pero no cualquier cripto. Bitcoin, la más conocida, es un titán para almacenar valor, pero para transacciones diarias necesita una segunda capa como Lightning Network, que procesa pagos instantáneos con comisiones ínfimas (menos de 0,01 USD por transacción en 2024). Alternativas como Bitcoin Cash (BCH) o Monero (XMR) ofrecen transacciones rápidas y, en el caso de XMR, un enfoque en la privacidad que hace temblar a los burócratas. Sin embargo, ninguna cripto servirá si los comercios y las personas no las adoptan. En Argentina, por ejemplo, solo el 1,5% de las transacciones minoristas en 2024 usaron criptomonedas, según Chainalysis. La libertad financiera no llega sola: hay que construirla.
El futuro es ahora El dinero es poder, y quien controla el dinero controla tu vida. Mientras Milei en Argentina te devuelve las llaves de tus dólares, en Europa y Chile te atan las manos con leyes, regulaciones y monedas digitales. La pregunta no es si quieres libertad, sino si estás dispuesto a pelear por ella. Usa efectivo, explora cripto, pero sobre todo, no dejes que el Gran Hermano decida por ti. Porque una vez que el Estado mete la mano en tu bolsillo, no la saca nunca.
-
 @ 94c2fd25:4fb53087
2025-06-05 06:41:55
@ 94c2fd25:4fb53087
2025-06-05 06:41:55EV8 không chỉ đơn thuần là một nền tảng cung cấp dịch vụ đa dạng mà còn là một biểu tượng của phong cách sống hiện đại, thuận tiện và thân thiện với môi trường. Với giao diện thân thiện và quy trình đăng ký, xác thực nhanh chóng, EV8 mang đến cho người dùng một trải nghiệm dễ dàng, giúp họ tiết kiệm thời gian trong cuộc sống bận rộn ngày nay. Các tính năng hỗ trợ thanh toán đa dạng như chuyển khoản ngân hàng, ví điện tử, và thẻ quốc tế tạo điều kiện thuận lợi cho mọi đối tượng sử dụng. Điều này góp phần thay đổi thói quen tiêu dùng của người dùng, từ những hành động đơn giản như nạp tiền, rút tiền, cho đến việc lựa chọn các dịch vụ phù hợp với nhu cầu cá nhân. EV8 giúp người dùng tiếp cận công nghệ một cách nhẹ nhàng, loại bỏ những trở ngại truyền thống, qua đó thúc đẩy sự phát triển của một xã hội số năng động và hiệu quả hơn.
Không chỉ tập trung vào tiện ích cá nhân, EV8 còn đóng vai trò quan trọng trong việc xây dựng cộng đồng bền vững và kết nối. Qua các chương trình ưu đãi, sự kiện hấp dẫn và hệ thống hỗ trợ khách hàng chuyên nghiệp, EV8 tạo nên sự gắn kết giữa người dùng và nền tảng, giúp họ cảm thấy được đồng hành và hỗ trợ mọi lúc mọi nơi. Những tính năng thông minh như quản lý năng lượng, theo dõi hoạt động và nhận thưởng qua các trò chơi cũng góp phần nâng cao nhận thức về sự cân bằng giữa giải trí và trách nhiệm trong cuộc sống. Từ đó, EV8 không chỉ là công cụ hỗ trợ mà còn là nguồn cảm hứng thúc đẩy người dùng sống chủ động, tích cực và thân thiện với môi trường trong kỷ nguyên số hóa ngày nay.
-
 @ 9e69e420:d12360c2
2025-02-01 11:16:04
@ 9e69e420:d12360c2
2025-02-01 11:16:04Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.

CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language.
One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse.
-
 @ 45ea632c:bb0b4fa1
2025-06-05 05:58:06
@ 45ea632c:bb0b4fa1
2025-06-05 05:58:06A plataforma 55BB chegou para transformar a maneira como os jogadores brasileiros se divertem no universo online. Com uma interface moderna, navegação intuitiva e uma grande variedade de jogos envolventes, a 55BB se destaca como uma das principais opções para quem busca diversão, emoção e praticidade em um só lugar.
Desde o primeiro acesso, a 55BB impressiona pela organização e design visual. O site é leve, rápido e funciona perfeitamente tanto em computadores quanto em dispositivos móveis. Isso significa que o jogador pode acessar seus jogos favoritos a qualquer hora e de qualquer lugar, com total comodidade e segurança.
Variedade de Jogos para Todos os Gostos Um dos grandes diferenciais da 55BB é sua ampla seleção de jogos. A plataforma oferece títulos que atendem a todos os perfis de jogadores — dos iniciantes aos mais experientes. Entre os jogos mais populares estão os slots, jogos de cartas como poker e baccarat, além de versões ao vivo com crupiês reais que proporcionam uma experiência imersiva e autêntica.
Os slots disponíveis na 55bbsão desenvolvidos por provedores de renome internacional, garantindo gráficos de alta qualidade, trilhas sonoras envolventes e recursos especiais que tornam cada rodada ainda mais empolgante. Além disso, a plataforma atualiza constantemente seu catálogo com novos lançamentos, mantendo a experiência sempre fresca e atrativa.
Já os fãs de jogos de mesa encontram na 55BB uma gama variada de opções clássicas e modernas. É possível escolher entre diferentes versões de roleta, blackjack e outros jogos tradicionais que exigem tanto sorte quanto estratégia. Tudo isso com transmissões ao vivo em alta definição e interações em tempo real, o que torna a experiência ainda mais próxima da realidade.
Experiência do Jogador: Segurança, Suporte e Bonificações Na 55BB, o jogador é tratado com prioridade. A plataforma conta com um sistema de segurança avançado que protege todos os dados pessoais e financeiros dos usuários. Todas as transações são criptografadas e seguem os padrões internacionais de proteção digital.
Outro ponto forte é o suporte ao cliente. A equipe de atendimento da 55BB está disponível 24 horas por dia, sete dias por semana, pronta para resolver dúvidas e auxiliar em qualquer necessidade. O atendimento pode ser feito via chat ao vivo ou e-mail, e sempre com respostas rápidas e claras.
Além disso, a 55BB oferece diversas promoções e bonificações exclusivas para seus usuários. Novos jogadores recebem recompensas logo após o cadastro, e há programas de fidelidade e desafios semanais que garantem prêmios extras. Tudo isso contribui para uma experiência mais gratificante e estimulante.
Conclusão A 55BB não é apenas uma plataforma de jogos online — é um verdadeiro ambiente de entretenimento digital pensado para o público brasileiro. Com jogos de alta qualidade, atendimento eficiente, segurança robusta e promoções atrativas, a 55BB se consolida como uma das melhores opções para quem busca diversão e emoção com responsabilidade.
Se você ainda não conhece a 55BB, vale a pena experimentar. Prepare-se para descobrir uma nova forma de jogar, ganhar e se entreter, tudo na palma da sua mão.
-
 @ 2ed3596e:98b4cc78
2025-06-04 20:06:07
@ 2ed3596e:98b4cc78
2025-06-04 20:06:07Bitcoin Well recently sat down with Bitcoin News for a conversation about our mission to empower financial independence through Bitcoin. Founder and CEO Adam O’Brien shared how a frustrating experience purchasing bitcoin in 2013 led to the creation of one of Canada’s largest bitcoin ATM networks—and ultimately, a broader mission to help people replace traditional banks with self-custodied bitcoin.
From building out our Bitcoin portal to navigating life fully de-banked, Adam discussed how Bitcoin Well is creating tools for everyday use—paying bills, receiving paychecks, and living sovereignly. Read the full conversation to understand why we’re proud to be leading the charge for freedom-minded Bitcoiners across Canada and beyond.
About Bitcoin Well:
Bitcoin Well is a Canadian company on a mission to enable financial independence through the use of Bitcoin. We offer tools and services that allow users to buy, sell, and use bitcoin in self-custody—without relying on traditional banks.
About Bitcoin News:
Bitcoin News Inc is a US-based media company dedicated to covering the latest in Bitcoin—from mining and wallets to its growing role in global liquidity. We deliver clear, insightful reporting to help readers navigate the shifting landscape of Bitcoin and digital finance.
-
 @ 0fa80bd3:ea7325de
2025-01-29 05:55:02
@ 0fa80bd3:ea7325de
2025-01-29 05:55:02The land that belongs to the indigenous peoples of Russia has been seized by a gang of killers who have unleashed a war of extermination. They wipe out anyone who refuses to conform to their rules. Those who disagree and stay behind are tortured and killed in prisons and labor camps. Those who flee lose their homeland, dissolve into foreign cultures, and fade away. And those who stand up to protect their people are attacked by the misled and deceived. The deceived die for the unchecked greed of a single dictator—thousands from both sides, people who just wanted to live, raise their kids, and build a future.
Now, they are forced to make an impossible choice: abandon their homeland or die. Some perish on the battlefield, others lose themselves in exile, stripped of their identity, scattered in a world that isn’t theirs.
There’s been endless debate about how to fix this, how to clear the field of the weeds that choke out every new sprout, every attempt at change. But the real problem? We can’t play by their rules. We can’t speak their language or use their weapons. We stand for humanity, and no matter how righteous our cause, we will not multiply suffering. Victory doesn’t come from matching the enemy—it comes from staying ahead, from using tools they haven’t mastered yet. That’s how wars are won.
Our only resource is the will of the people to rewrite the order of things. Historian Timothy Snyder once said that a nation cannot exist without a city. A city is where the most active part of a nation thrives. But the cities are occupied. The streets are watched. Gatherings are impossible. They control the money. They control the mail. They control the media. And any dissent is crushed before it can take root.
So I started asking myself: How do we stop this fragmentation? How do we create a space where people can rebuild their connections when they’re ready? How do we build a self-sustaining network, where everyone contributes and benefits proportionally, while keeping their freedom to leave intact? And more importantly—how do we make it spread, even in occupied territory?
In 2009, something historic happened: the internet got its own money. Thanks to Satoshi Nakamoto, the world took a massive leap forward. Bitcoin and decentralized ledgers shattered the idea that money must be controlled by the state. Now, to move or store value, all you need is an address and a key. A tiny string of text, easy to carry, impossible to seize.
That was the year money broke free. The state lost its grip. Its biggest weapon—physical currency—became irrelevant. Money became purely digital.
The internet was already a sanctuary for information, a place where people could connect and organize. But with Bitcoin, it evolved. Now, value itself could flow freely, beyond the reach of authorities.
Think about it: when seedlings are grown in controlled environments before being planted outside, they get stronger, survive longer, and bear fruit faster. That’s how we handle crops in harsh climates—nurture them until they’re ready for the wild.
Now, picture the internet as that controlled environment for ideas. Bitcoin? It’s the fertile soil that lets them grow. A testing ground for new models of interaction, where concepts can take root before they move into the real world. If nation-states are a battlefield, locked in a brutal war for territory, the internet is boundless. It can absorb any number of ideas, any number of people, and it doesn’t run out of space.
But for this ecosystem to thrive, people need safe ways to communicate, to share ideas, to build something real—without surveillance, without censorship, without the constant fear of being erased.
This is where Nostr comes in.
Nostr—"Notes and Other Stuff Transmitted by Relays"—is more than just a messaging protocol. It’s a new kind of city. One that no dictator can seize, no corporation can own, no government can shut down.
It’s built on decentralization, encryption, and individual control. Messages don’t pass through central servers—they are relayed through independent nodes, and users choose which ones to trust. There’s no master switch to shut it all down. Every person owns their identity, their data, their connections. And no one—no state, no tech giant, no algorithm—can silence them.
In a world where cities fall and governments fail, Nostr is a city that cannot be occupied. A place for ideas, for networks, for freedom. A city that grows stronger the more people build within it.
-
 @ 45ea632c:bb0b4fa1
2025-06-05 05:57:40
@ 45ea632c:bb0b4fa1
2025-06-05 05:57:40Se você está em busca de uma experiência completa de diversão digital com praticidade, segurança e uma ampla variedade de jogos, a TT999 é uma plataforma que merece sua atenção. Com uma interface moderna, navegação intuitiva e suporte ao jogador eficiente, o site tem se destacado no cenário brasileiro como uma das principais referências em entretenimento online.
Conheça a Plataforma TT999 A TT999 é mais do que apenas uma plataforma de jogos. Ela foi desenvolvida pensando na experiência do usuário, combinando tecnologia de ponta, gráficos de alta qualidade e uma estrutura funcional que agrada tanto novatos quanto jogadores experientes. Desde o momento em que o usuário acessa o site, é possível perceber a preocupação da plataforma em oferecer um ambiente seguro e acessível.
A inscrição é rápida, exigindo apenas informações básicas, e o processo de verificação é feito de forma simples e eficaz. Além disso, a TT999 oferece múltiplas opções de pagamento e saque, todas com criptografia avançada para garantir a segurança das transações.
Outro diferencial importante da tt999é a compatibilidade com diversos dispositivos. A plataforma pode ser acessada facilmente por computador, tablet ou smartphone, sem a necessidade de baixar aplicativos pesados. Isso garante flexibilidade para que o jogador possa se divertir a qualquer hora e em qualquer lugar.
Variedade de Jogos para Todos os Perfis Um dos grandes atrativos da TT999 é seu catálogo diversificado de jogos. A plataforma conta com centenas de opções que abrangem diferentes estilos e preferências. Entre os destaques estão os populares jogos de cartas, slots com diferentes temáticas, jogos de roleta, além de jogos ao vivo que oferecem uma interação em tempo real com apresentadores e outros jogadores.
Os slots são uma das categorias mais acessadas, especialmente por suas temáticas variadas e bônus atrativos. Já os jogos de cartas, como o pôquer e o bacará, exigem mais estratégia e atraem aqueles que gostam de desafios mais intensos.
A TT999 também se destaca pelos jogos ao vivo, que proporcionam uma experiência imersiva ao simular um ambiente de jogo real com câmeras em alta definição e interatividade em tempo real. Essa funcionalidade tem sido um diferencial importante para os jogadores brasileiros, que buscam uma atmosfera mais envolvente.
A Experiência do Jogador na TT999 Quem joga na TT999 logo percebe o cuidado da plataforma com a experiência do usuário. Desde o design responsivo até o atendimento ao cliente eficiente e multilíngue, tudo é feito para garantir que o jogador tenha uma jornada fluida e satisfatória.
O suporte está disponível 24 horas por dia, com atendimento via chat ao vivo, e-mail e FAQ detalhado. Os jogadores relatam que as respostas são rápidas e sempre objetivas, o que demonstra o comprometimento da equipe com a comunidade.
Além disso, a TT999 oferece promoções frequentes, bônus de boas-vindas, programas de fidelidade e recompensas personalizadas. Essas iniciativas não só incentivam o engajamento, mas também fazem com que os jogadores se sintam valorizados.
Conclusão A TT999 é uma plataforma completa para quem busca diversão online com qualidade, segurança e variedade. Seu compromisso com a inovação e a experiência do jogador tem conquistado o público brasileiro, tornando-a uma das principais referências em entretenimento digital. Se você ainda não conhece a TT999, esta pode ser a hora perfeita para explorar um novo mundo de possibilidades e jogos envolventes, tudo na palma da sua mão.
-
 @ ca76c778:e784c54b
2025-06-04 19:45:11
@ ca76c778:e784c54b
2025-06-04 19:45:11A few days ago I remembered video by Antonio Stappaerts(Artwod) on Youtube. And I thought to myself I want to be really good at drawing hands.\ In the video he explains something that, in my opinion, applies when learning just about anything.
If you've heard of the Dunning-Kruger effect then you know the first part.\ If you haven't, one begins learning something and on top of the first peak thinks oneself to be almost a master. And then one learns a little bit more and realizes how little skill one actually has.
 \
Now, what is really interesting is this. He points out that the second slope is made up of many smaller Dunning-Kruger effects. For example the effect will apply when learning: the basic shape of the figure, how to pose the figure, how draw the hands, the hair etc.
\
Now, what is really interesting is this. He points out that the second slope is made up of many smaller Dunning-Kruger effects. For example the effect will apply when learning: the basic shape of the figure, how to pose the figure, how draw the hands, the hair etc.So the way to climb the second hill is to understand and practice these smaller skills. And not just once or twice. You want to reach close to the second peak of each of the smaller skills.
And with that in mind I search for a good tutorial about drawing hands and got down to it(for the third time).
Step one was to learn pose and gesture using a grid shape.
https://cdn.satellite.earth/f55a9d1ef2fd687a9dce5ceee5e05a1b666c436509e264ddbac4d260b99e882a.jpg
https://cdn.satellite.earth/1b5524635c20ee4869f4860c982deea469cb87be7ad7b404e1777497b5a4fbd4.jpg
https://cdn.satellite.earth/35652251243ffd8c495b855c319d27da0c193ff2e951591f0a9f1b35aad39b29.jpg
https://cdn.satellite.earth/68f55979d102b4ebe55177842c6d9ab2ab30b95f926441429d977b47fae925c3.jpg
Step two. Practice the basic forms for the palm and fingers.\ I got carried away and drew some hands.
https://cdn.satellite.earth/48b400f72e35d078368149f00182cb58e606ddd16f6db4e7789c1431c28d44a0.jpg
Step three. learn the measurements.
https://cdn.satellite.earth/75c9b82da90ef50d17f698dd7b1eadc223b74a019a702a4617ed7d321646a87c.jpg
Step four. Understand the fingers.
https://cdn.satellite.earth/e33f9f3f9217bf5e3e206e96dfe764eba09b9fb3c10b450bb9c8a4075e3c1ec8.jpg
Step five. Learn about the thumb and put it all together. Drawing from reference and imagination.
https://cdn.satellite.earth/b2dd9c1cc1045dde021272199818b0db331e71a603c5900122aa850eb2d4148a.jpg
https://cdn.satellite.earth/8f5647ae9e148ad6217c106b5b69cf231384475e0a0eedf210bd149f75ade0b7.jpg
-
 @ b2caa9b3:9eab0fb5
2025-06-04 19:50:29
@ b2caa9b3:9eab0fb5
2025-06-04 19:50:29If you'd like to connect with me on XMPP, you're very welcome! I first used it many years ago, and now I've returned to it — and I'm really glad I did.
XMPP is a secure and privacy-friendly way to communicate. It's spam-resistant: messages only go through once you've accepted a contact request. To request a connection, just send me a message.
One of the great things about XMPP is that you have control over encryption. You can choose to use strong encryption like PGP or OMEMO, or even no encryption at all — it's entirely up to you. Your messages aren’t tied to any one company or service.
There are many apps (called clients) you can use with XMPP, and you’re not locked into a single one that monitors or sells your data. XMPP is an open protocol, which means freedom of choice and better privacy.
My XMPP username is: rubenstorm@c0nnect.de
I’ve also been much less active on Facebook, Instagram, and other social media. That’s because I’ve shifted from platforms to protocols — more decentralized, censorship-resistant tools that put users in control. I started exploring these about two years ago and haven’t looked back.
If you’re interested in learning more or want help getting started, feel free to reach out. Just message me using any XMPP client — I’ll be happy to connect!
-
 @ a5ee4475:2ca75401
2025-06-04 18:11:52
@ a5ee4475:2ca75401
2025-06-04 18:11:52clients #link #list #english #article #finalversion #descentralismo
*These clients are generally applications on the Nostr network that allow you to use the same account, regardless of the app used, keeping your messages and profile intact.
**However, you may need to meet certain requirements regarding access and account NIP for some clients, so that you can access them securely and use their features correctly.
CLIENTS
Twitter like
- Nostrmo - [source] 🌐💻(🐧🪟🍎)🍎🤖(on zapstore)
- Coracle - Super App [source] 🌐🤖(on zapstore)
- Amethyst - Super App with note edit, delete and other stuff with Tor [source] 🤖(on zapstore)
- Primal - Social and wallet [source] 🌐🍎🤖(on zapstore)
- Iris - [source] 🌐🤖🍎
- Current - [source] 🤖🍎
- FreeFrom 🤖🍎
- Openvibe - Nostr and others (new Plebstr) [source] 🤖🍎
- Snort 🌐(🤖[early access]) [onion] [source]
- Damus 🍎 [source]
- Nos 🍎 [source]
- Nostur 🍎 [source]
- NostrBand 🌐 [info] [source]
- Yana [source] 🌐💻(🐧) 🍎🤖(on zapstore)
- Nostribe [on development] 🌐 [source]
- Lume 💻(🐧🪟🍎) [info] [source]
- Gossip - [source] 💻(🐧🪟🍎)
- noStrudel - Gamified Experience [onion] [info/source] 🌐
- [Nostrudel Next] - [onion]
- moStard - Nostrudel with Monero [onion] [info/source] 🌐
- Camelus - [source] 🤖 [early access]
Community
- CCNS - Community Curated Nostr Stuff [source]
- Nostr Kiwi [creator] 🌐
- Satellite [info] 🌐
- Flotilla - [source] 🌐🐧🤖(on zapstore)
- Chachi - [source] 🌐
- Futr - Coded in haskell [source] 🐧 (others soon)
- Soapbox - Comunnity server [info] [source] 🌐
- Ditto - Soapbox community server 🌐 [source] 🌐
- Cobrafuma - Nostr brazilian community on Ditto [info] 🌐
- Zapddit - Reddit like [source] 🌐
- Voyage (Reddit like) [on development] 🤖
Wiki
- Wikifreedia - Wiki Dark mode [source] 🌐
- Wikinostr - Wiki with tabs clear mode [source] 🌐
- Wikistr - Wiki clear mode [info] [source] 🌐
Search
- Keychat - Signal-like chat with AI and browser [source] 💻(🐧🪟🍎) - 📱(🍎🤖{on zapstore})
- Spring - Browser for Nostr apps and other sites [source] 🤖 (on zapstore)
- Advanced nostr search - Advanced note search by isolated terms related to a npub profile [source] 🌐
- Nos Today - Global note search by isolated terms [info] [source] 🌐
- Nostr Search Engine - API for Nostr clients [source]
- Ntrends - Trending notes and profiles 🌐
Website
- Nsite - Nostr Site [onion] [info] [source]
- Nsite Gateway - Nostr Site Gateway [source]
- Npub pro - Your site on Nostr [source]
App Store
ZapStore - Permitionless App Store [source] 🤖 💻(🐧🍎)
Video and Live Streaming
- Flare - Youtube like 🌐 [source]
- ZapStream - Lives, videos, shorts and zaps (NIP-53) [source] 🌐 🤖(lives only | Amber | on zapstore)
- StreamCat - [source code dont found]
- Shosho - Stream your camera [source] 🤖(on zapstore)
- Swae - Live streaming [source] (on development) ⏳
Post Aggregator - Kinostr - Nostr Cinema with #kinostr [english] [author] 🌐 - Stremstr - Nostr Cinema with #kinostr [english] [source] 🤖
Link Agreggator - Kinostr - #kinostr - Nostr Cinema Profile with links [English] - Equinox - Nostr Cinema Community with links [Portuguese]
Audio and Podcast Transmission
- Castr - Your npub as podcast feed [source]
- Nostr Nests - Audio Chats [source] 🌐
- Fountain - Podcast [source] 🤖🍎
- Corny Chat - Audio Chat [source] 🌐
Music
- Tidal - Music Streaming [source] [about] [info] 🤖🍎🌐
- Wavlake - Music Streaming [source] 🌐(🤖🍎 [early access])
- Tunestr - Musical Events [source] [about] 🌐
- Stemstr - Musical Colab (paid to post) [source] [about] 🌐
Images
- Lumina - Trending images and pictures [source] 🌐
- Pinstr - Pinterest like [source] 🌐
- Slidestr - DeviantArt like [source] 🌐
- Memestr - ifunny like [source] 🌐
Download and Upload
Documents, graphics and tables
- Mindstr - Mind maps [source] 🌐
- Docstr - Share Docs [info] [source] 🌐
- Formstr - Share Forms [info] 🌐
- Sheetstr - Share Spreadsheets [source] 🌐
- Slide Maker - Share slides 🌐 [Advice: Slide Maker https://zaplinks.lol/ site is down]
Health
- Sobrkey - Sobriety and mental health [source] 🌐
- Runstr - Running app [source] 🌐
- NosFabrica - Finding ways for your health data 🌐
- LazerEyes - Eye prescription by DM [source] 🌐
Forum
- OddBean - Hacker News like [info] [source] 🌐
- LowEnt - Forum [info] 🌐
- Swarmstr - Q&A / FAQ [info] 🌐
- Staker News - Hacker News like 🌐 [info]
Direct Messenges (DM)
- 0xchat 🤖🍎 [source]
- Nostr Chat 🌐🍎 [source]
- Blowater 🌐 [source]
- Anigma (new nostrgram) - Telegram based [on development] [source]
Reading
- Oracolo - A minimalist Nostr html blog [source]
- nRSS - Nostr RSS reader 🌐
- Highlighter - Insights with a highlighted read [info] 🌐
- Zephyr - Calming to Read [info] 🌐
- Flycat - Clean and Healthy Feed [info] 🌐
- Nosta - Check Profiles [on development] [info] 🌐
- Alexandria - e-Reader and Nostr Knowledge Base (NKB) [source] 🌐
Writing
- Habla - Blog [info] 🌐
- Blogstack - Blog [info]🌐
- YakiHonne - Articles and News [info] 🌐🍎🤖(on zapstore)
Lists
- Following - Users list [source] 🌐
- Nostr Unfollower - Nostr Unfollower
- Listr - Lists [source] 🌐
- Nostr potatoes - Movies List [source] 💻(numpy)
Market and Jobs
- Shopstr - Buy and Sell [onion] [source] 🌐
- Nostr Market - Buy and Sell 🌐
- Plebeian Market - Buy and Sell [source] 🌐
- Ostrich Work - Jobs [source] 🌐
- Nostrocket - Jobs [source] 🌐
Data Vending Machines - DVM (NIP90)
(Data-processing tools)
Games
- Chesstr - Chess 🌐 [source]
- Jestr - Chess [source] 🌐
- Snakestr - Snake game [source] 🌐
- Snakes on a Relay - Multiplayer Snake game like slither.io [source] 🌐
ENGINES - DEG Mods - Decentralized Game Mods [info] [source] 🌐 - NG Engine - Nostr Game Engine [source] 🌐 - JmonkeyEngine - Java game engine [source] 🌐
Customization
Like other Services
- Olas - Instagram like [source] 🌐🍎🤖(on zapstore)
- Nostree - Linktree like 🌐
- Rabbit - TweetDeck like [info] 🌐
- Zaplinks - Nostr links 🌐
- Omeglestr - Omegle-like Random Chats [source] 🌐
General Uses
- Njump - HTML text gateway source 🌐
- Filestr - HTML midia gateway [source] 🌐
- W3 - Nostr URL shortener [source] 🌐
- Playground - Test Nostr filters [source] 🌐
Places
- Wherostr - Travel and show where you are
- Arc Map (Mapstr) - Bitcoin Map [info]
Driver and Delivery
- RoadRunner - Uber like [on development] ⏱️
- Nostrlivery - iFood like [on development] ⏱️
⚠️ SCAM ⚠️ | Arcade City - Uber like [source]
OTHER STUFF
Lightning Wallets (zap)
- Wallet of Satoshi - Simplest Lightning Wallet [info] 🤖🍎
- Coinos - Web wallet and Nostr client [source] 🌐
- Alby - Native and extension [info] [source] 🌐
- Minibits - Cashu mobile wallet [info] 🤖
- LNbits - App and extension [source] 🤖🍎💻
- Zeus - [info] [source] 🤖🍎
- Blink - Open source custodial wallet (KYC over 1000 usd) [source] 🤖🍎
⚠️ ZBD - Zap Gaming wallet and no more Social [closed source] [info] [some resources] 🤖 ⚠️ ZBD suddenly canceled my account for alleged Terms of Service violations, gives me no explanation and won't let me withdraw my money ⚠️
Without Zap - Wassabi Wallet - Privacy-focused and non-custodial with Nostr Update Manager [source]
Exchange
Media Server (Upload Links)
audio, image and video
Connected with Nostr (NIP):
- Nostr Build - Free and paid Upload [info] [source] 🌐
- NostrMedia - Written in Go with Nip 96 / Blossom (free and paid) [info] [source]
- Nostr Check - [info] [source] 🌐
- NostPic - [info] [source] 🌐
- Sovbit - Free and paid upload [info] [source] 🌐
- Voidcat - Nip-96 and Blossom [source] 🌐
- Primal Media - Primal Media Uploader [source] 🌐
Blossom - Your Media Safer
- Primal Blossom 🌐
- NostrBuild Blossom - Free upload (max 100MiB) and paid [info] [source] 🌐
Paid Upload Only
- Satellite CDN - prepaid upload (max 5GB each) [info] [source] 🌐
Without Nostr NIP:
- Pomf - Upload larger videos (max 1GB) [source]
- Catbox - max 200 MB [source]
- x0 - max 512 MiB [source]
Donation and payments
- Zapper - Easy Zaps [source] 🌐
- Autozap [source] 🌐
- Zapmeacoffee 🌐
- Nostr Zap 💻(numpy)
- Creatr - Creators subscription 🌐
- Geyzer - Crowdfunding [info] [source] 🌐
- Heya! - Crowdfunding [source]
Security
- Secret Border - Generate offline keys 💻(java)
- Umbrel - Your private relay [source] 🌐
Key signing/login and Extension
- Amber - Key signing [source] 🤖(on zapstore)
- Nowser - Account access keys 📱(🤖🍎) 💻(🐧🍎🪟)
- Nos2x - Account access keys 🌐
- Nsec.app 🌐 [info]
- Lume - [info] [source] 🐧🪟🍎
- Satcom - Share files to discuss - [info] 🌐
- KeysBand - Multi-key signing [source] 🌐
Code
- Stacks - AI Templates [info] [source] 🌐
- Nostrify - Share Nostr Frameworks 🌐
- Git Workshop (github like) [experimental] 🌐
- Gitstr (github like) [on development] ⏱️
- Osty [on development] [info] 🌐
- Python Nostr - Python Library for Nostr
- Sybil - Creating, managing and test Nostr events [on development] ⏱️
Relay Check and Cloud
- Nostr Watch - See your relay speed 🌐
- NosDrive - Nostr Relay that saves to Google Drive
Bidges and Getways
- Matrixtr Bridge - Between Matrix & Nostr
- Mostr - Between Nostr & Fediverse
- Nostrss - RSS to Nostr
- Rsslay - Optimized RSS to Nostr [source]
- Atomstr - RSS/Atom to Nostr [source]
Useful Profiles and Trends
nostr-voice - Voice note (just some clients)
NOT RELATED TO NOSTR
Voca - Text-to-Speech App for GrapheneOS [source] 🤖(on zapstore)
Android Keyboards
Personal notes and texts
Front-ends
- Nitter - Twitter / X without your data [source]
- NewPipe - Youtube, Peertube and others, without account & your data [source] 🤖
- Piped - Youtube web without you data [source] 🌐
Other Services
- Brave - Browser [source]
- DuckDuckGo - Search [source]
- LLMA - Meta - Meta open source AI [source]
- DuckDuckGo AI Chat - Famous AIs without Login [source]
- Proton Mail - Mail [source]
Other open source index: Degoogled Apps
Some other Nostr index on:
-
 @ 6316050a:a5e43cbe
2025-06-04 14:24:01
@ 6316050a:a5e43cbe
2025-06-04 14:24:01Contexto
En el Grupo de Teoría y Simulación en Materia Blanda estudiamos sistemas poliméricos, interfaces y sistemas coloidales a escala nanoscópica. Estos pueden estar en equilibrio o presentar flujo de partículas o calor y son de interés en ciencia básica y aplicada en campos como micro y nano-fluídica, aplicaciones a transferencia de calor y máquinas moleculares. Una característica central es que la temperatura juega un rol importante y existe una competencia entre entropía y energía. Esto suele dar lugar a transiciones de fases u otros cambios cualitativos del comportamiento del sistema.
Herramientas
Usamos simulación computacional y herramientas teóricas, con énfasis en conceptos de mecánica estadística, que permiten estudiar variados sistemas en diferentes situaciones físicas. Estudiamos a estos sistemas en condiciones de equilibrio termodinámico o también cómo es su comportamiento cuando se inducen flujos o se los somete a campos externos. (fuera de equilibrio)
Proponemos el siguiente tema de Tesis de Licenciatura en física
Simulación de transferencia de calor en nanocanales con paredes modificadas por polímeros

 Izquierda: Nano- con una interfaz líquido vapor canal y un flujo estacionario de calor, provocado por la diferencia de temperatura de las paredes. Derecha: Puente de líquido inducido por la presencia de polímeros semi-flexibles. Ambas imágenes obtenidas de simulaciones de dinámica molecular.
Izquierda: Nano- con una interfaz líquido vapor canal y un flujo estacionario de calor, provocado por la diferencia de temperatura de las paredes. Derecha: Puente de líquido inducido por la presencia de polímeros semi-flexibles. Ambas imágenes obtenidas de simulaciones de dinámica molecular. Los fenómenos de transferencia de calor tienen una gran importancia en un amplísimo rango de aplicaciones como los procesos de generación y conversión de energía y son cruciales para el enfriamiento de motores y dispositivos electrónicos. Estas aplicaciones requerirán en el futuro un funcionamiento a mayor densidad de energía, y por lo tanto, mayor generación de calor, que deberá ser removido más eficientemente. En particular, los fenómenos de cambio de fases, como la ebullición nucleada, tienen aplicaciones en plantas de potencia eléctrica, desalinización térmica, enfriamiento de chips electrónicos y recuperación de calor desechado, entre muchas otras. Uno de los desafíos más importantes para continuar la reducción de tamaño de los dispositivos electrónicos es aumentar su densidad de potencia de operación y para ello se debe lograr una extracción eficiente del calor generado. La transferencia de calor es relevante también en aplicaciones a escalas espaciales mayores, como en la generación de energía eléctrica en centrales térmicas y nucleares. En las centrales nucleares de generación IV es necesario aumentar el calor transportado por unidad de tiempo y mejorar la eficiencia de los intercambiadores de calor. Estos procesos de transporte térmico distan de comprenderse a nivel básico, porque tienen una gran complejidad en tanto que son fenómenos fuera de equilibrio con cambios de fases.
Se propone estudiar la transferencia de calor en un nanocanal que presenta una interfaz líquido-vapor.
Estudiaremos los detalles de cómo cambian con el tiempo las características de la evaporación de una interfaz y las propiedades térmicas cuando se modifica la pared con polímeros u otras moléculas en el seno del líquido. Analizaremos también la rectificación del flujo de calor, pensando al nano-canal como un diodo térmico. Realizaremos simulaciones de dinámica molecular en clusters de supercómputo para estudiar estos sistemas en distintas condiciones físicas. Si tienen interés en tener más detalles, no duden en contactarnos.Contacto: Claudio Pastorino (claudiopastorino .... cnea.gob.ar ; IG, X: @clopasto; Nostr: @clopasto
¿Qué se aprenderá en esta Tesis principalmente?
Estas línea de trabajo es teórico-numérica , con una parte importante de simulación computacional. Involucra principalmente conceptos de: * Mecánica estadística (Física Teórica 3 en DF-UBA), * Materia condensada en general y materia blanda. * Fundamentos y uso de simulación computacional: Dinámica Molecular, Dissipative Particle Dynamics y/o Monte Carlo, * No se requieren conocimientos previos de computación, pero sí interés en el uso y creación de programas, para plantear y calcular propiedades de los sistemas físicos. * Se trabajará con * Linux, Python, Bash, Awk. * Clusters de super-cómputo, High Performance Computing. * Herramientas de posprocesamiento.
Referencias
- Heat flow through a liquid–vapor interface in a nano-channel: the effect of end-grafting polymers on a wall , Claudio Pastorino, Ignacio Urrutia, María Fiora y Federico Condado, J. Phys. Cond. Matt. 34:344004
- Boiling and quenching heat transfer advancement by nanoscale surface modification Hu, Xu, Cheng, Zhao, Ziegler and Chung. Scientific Reports 7:6117 (2017)
-
 @ 6be5cc06:5259daf0
2025-01-21 20:58:37
@ 6be5cc06:5259daf0
2025-01-21 20:58:37A seguir, veja como instalar e configurar o Privoxy no Pop!_OS.
1. Instalar o Tor e o Privoxy
Abra o terminal e execute:
bash sudo apt update sudo apt install tor privoxyExplicação:
- Tor: Roteia o tráfego pela rede Tor.
- Privoxy: Proxy avançado que intermedia a conexão entre aplicativos e o Tor.
2. Configurar o Privoxy
Abra o arquivo de configuração do Privoxy:
bash sudo nano /etc/privoxy/configNavegue até a última linha (atalho:
Ctrl+/depoisCtrl+Vpara navegar diretamente até a última linha) e insira:bash forward-socks5 / 127.0.0.1:9050 .Isso faz com que o Privoxy envie todo o tráfego para o Tor através da porta 9050.
Salve (
CTRL+OeEnter) e feche (CTRL+X) o arquivo.
3. Iniciar o Tor e o Privoxy
Agora, inicie e habilite os serviços:
bash sudo systemctl start tor sudo systemctl start privoxy sudo systemctl enable tor sudo systemctl enable privoxyExplicação:
- start: Inicia os serviços.
- enable: Faz com que iniciem automaticamente ao ligar o PC.
4. Configurar o Navegador Firefox
Para usar a rede Tor com o Firefox:
- Abra o Firefox.
- Acesse Configurações → Configurar conexão.
- Selecione Configuração manual de proxy.
- Configure assim:
- Proxy HTTP:
127.0.0.1 - Porta:
8118(porta padrão do Privoxy) - Domínio SOCKS (v5):
127.0.0.1 - Porta:
9050
- Proxy HTTP:
- Marque a opção "Usar este proxy também em HTTPS".
- Clique em OK.
5. Verificar a Conexão com o Tor
Abra o navegador e acesse:
text https://check.torproject.org/Se aparecer a mensagem "Congratulations. This browser is configured to use Tor.", a configuração está correta.
Dicas Extras
- Privoxy pode ser ajustado para bloquear anúncios e rastreadores.
- Outros aplicativos também podem ser configurados para usar o Privoxy.
-
 @ 9e69e420:d12360c2
2025-01-21 19:31:48
@ 9e69e420:d12360c2
2025-01-21 19:31:48Oregano oil is a potent natural compound that offers numerous scientifically-supported health benefits.
Active Compounds
The oil's therapeutic properties stem from its key bioactive components: - Carvacrol and thymol (primary active compounds) - Polyphenols and other antioxidant
Antimicrobial Properties
Bacterial Protection The oil demonstrates powerful antibacterial effects, even against antibiotic-resistant strains like MRSA and other harmful bacteria. Studies show it effectively inactivates various pathogenic bacteria without developing resistance.
Antifungal Effects It effectively combats fungal infections, particularly Candida-related conditions like oral thrush, athlete's foot, and nail infections.
Digestive Health Benefits
Oregano oil supports digestive wellness by: - Promoting gastric juice secretion and enzyme production - Helping treat Small Intestinal Bacterial Overgrowth (SIBO) - Managing digestive discomfort, bloating, and IBS symptoms
Anti-inflammatory and Antioxidant Effects
The oil provides significant protective benefits through: - Powerful antioxidant activity that fights free radicals - Reduction of inflammatory markers in the body - Protection against oxidative stress-related conditions
Respiratory Support
It aids respiratory health by: - Loosening mucus and phlegm - Suppressing coughs and throat irritation - Supporting overall respiratory tract function
Additional Benefits
Skin Health - Improves conditions like psoriasis, acne, and eczema - Supports wound healing through antibacterial action - Provides anti-aging benefits through antioxidant properties
Cardiovascular Health Studies show oregano oil may help: - Reduce LDL (bad) cholesterol levels - Support overall heart health
Pain Management The oil demonstrates effectiveness in: - Reducing inflammation-related pain - Managing muscle discomfort - Providing topical pain relief
Safety Note
While oregano oil is generally safe, it's highly concentrated and should be properly diluted before use Consult a healthcare provider before starting supplementation, especially if taking other medications.
-
 @ e136fbe5:b6e8325d
2025-06-04 10:02:38
@ e136fbe5:b6e8325d
2025-06-04 10:02:38Trong thời đại công nghệ số và đô thị hóa nhanh chóng, Việt Nam đang chứng kiến làn sóng chuyển mình mạnh mẽ từ các thành phố truyền thống sang những khu đô thị thông minh với hệ thống hạ tầng hiện đại, kết nối số và lấy người dân làm trung tâm. Trong bối cảnh đó, EV8 đóng vai trò ngày càng quan trọng khi trở thành giải pháp hỗ trợ thiết thực cho mục tiêu phát triển đô thị bền vững, thân thiện với môi trường và thuận tiện cho người dân. Xe điện EV8 không chỉ giúp giảm thiểu ô nhiễm không khí, tiếng ồn mà còn tối ưu hóa quá trình di chuyển trong nội đô với công nghệ định vị, quản lý năng lượng và kết nối tức thời thông qua nền tảng số. Khi hạ tầng giao thông thông minh đang dần được hoàn thiện, EV8 kết hợp cùng các hệ thống đèn tín hiệu, trạm sạc công cộng, ứng dụng điều hướng, và dữ liệu thời gian thực để mang lại trải nghiệm di chuyển hiệu quả, an toàn và dễ dàng hơn. Điều này giúp người dùng không chỉ tiết kiệm chi phí mà còn chủ động trong từng hành trình, đồng thời nâng cao chất lượng sống trong môi trường đô thị văn minh. Tính linh hoạt, thân thiện và khả năng tích hợp công nghệ chính là những yếu tố khiến EV8 trở thành sự lựa chọn lý tưởng cho cư dân các thành phố thông minh tương lai.
Không dừng lại ở khía cạnh giao thông, EV8 còn đóng góp vào việc xây dựng một hệ sinh thái đô thị đa chiều với khả năng tương tác giữa con người và công nghệ. Nền tảng EV8 không chỉ cung cấp phương tiện di chuyển mà còn kết nối người dùng với mạng lưới dịch vụ tiện ích đô thị như thanh toán điện tử, quản lý năng lượng cá nhân, theo dõi chỉ số môi trường xung quanh, và nhận cảnh báo giao thông thông minh. Qua đó, EV8 góp phần thúc đẩy hành vi sống xanh, có trách nhiệm, đồng thời khuyến khích người dân sử dụng công nghệ để giải quyết các vấn đề của đời sống hàng ngày. Việc EV8 đồng hành cùng các đô thị thông minh không chỉ mang ý nghĩa công nghệ mà còn là sự cam kết về giá trị cộng đồng – tạo ra một môi trường sống hiệu quả, bền vững và kết nối cao. Đặc biệt, những chiến dịch cộng đồng và chương trình ưu đãi tích hợp như tích điểm sử dụng xanh, hoàn tiền khi tham gia các hoạt động bảo vệ môi trường, hay hỗ trợ tài chính cho người dân chuyển đổi sang xe điện đều là minh chứng cho tầm nhìn dài hạn của EV8 trong việc đồng hành cùng quá trình xây dựng thành phố tương lai. Nhờ sự hiện diện của EV8, các đô thị tại Việt Nam đang tiến gần hơn đến chuẩn mực sống thông minh – nơi công nghệ phục vụ con người một cách thiết thực và bền vững, đồng thời khẳng định vai trò tiên phong của EV8 trong việc kiến tạo tương lai đô thị số.
-
 @ e2c72a5a:bfacb2ee
2025-06-06 01:42:46
@ e2c72a5a:bfacb2ee
2025-06-06 01:42:46North Korea's digital heist reveals the dark side of crypto's borderless nature. The US Justice Department is hunting $7.7 million in stolen cryptocurrency and NFTs allegedly laundered through an elaborate scheme involving North Korean IT workers posing as legitimate freelancers. This isn't just another hack—it's a sophisticated state-sponsored operation exploiting the very features that make crypto revolutionary: anonymity and borderless transactions. While we celebrate crypto's ability to transcend boundaries, this case exposes how those same qualities create perfect conditions for rogue nations to fund weapons programs and evade sanctions. The crypto industry faces a critical balancing act: how do we preserve financial freedom while preventing bad actors from exploiting the system? Perhaps the solution isn't more regulation but smarter blockchain analytics and international cooperation. What security measures would you support that don't compromise crypto's core principles?
-
 @ 6be5cc06:5259daf0
2025-01-21 01:51:46
@ 6be5cc06:5259daf0
2025-01-21 01:51:46Bitcoin: Um sistema de dinheiro eletrônico direto entre pessoas.
Satoshi Nakamoto
satoshin@gmx.com
www.bitcoin.org
Resumo
O Bitcoin é uma forma de dinheiro digital que permite pagamentos diretos entre pessoas, sem a necessidade de um banco ou instituição financeira. Ele resolve um problema chamado gasto duplo, que ocorre quando alguém tenta gastar o mesmo dinheiro duas vezes. Para evitar isso, o Bitcoin usa uma rede descentralizada onde todos trabalham juntos para verificar e registrar as transações.
As transações são registradas em um livro público chamado blockchain, protegido por uma técnica chamada Prova de Trabalho. Essa técnica cria uma cadeia de registros que não pode ser alterada sem refazer todo o trabalho já feito. Essa cadeia é mantida pelos computadores que participam da rede, e a mais longa é considerada a verdadeira.
Enquanto a maior parte do poder computacional da rede for controlada por participantes honestos, o sistema continuará funcionando de forma segura. A rede é flexível, permitindo que qualquer pessoa entre ou saia a qualquer momento, sempre confiando na cadeia mais longa como prova do que aconteceu.
1. Introdução
Hoje, quase todos os pagamentos feitos pela internet dependem de bancos ou empresas como processadores de pagamento (cartões de crédito, por exemplo) para funcionar. Embora esse sistema seja útil, ele tem problemas importantes porque é baseado em confiança.
Primeiro, essas empresas podem reverter pagamentos, o que é útil em caso de erros, mas cria custos e incertezas. Isso faz com que pequenas transações, como pagar centavos por um serviço, se tornem inviáveis. Além disso, os comerciantes são obrigados a desconfiar dos clientes, pedindo informações extras e aceitando fraudes como algo inevitável.
Esses problemas não existem no dinheiro físico, como o papel-moeda, onde o pagamento é final e direto entre as partes. No entanto, não temos como enviar dinheiro físico pela internet sem depender de um intermediário confiável.
O que precisamos é de um sistema de pagamento eletrônico baseado em provas matemáticas, não em confiança. Esse sistema permitiria que qualquer pessoa enviasse dinheiro diretamente para outra, sem depender de bancos ou processadores de pagamento. Além disso, as transações seriam irreversíveis, protegendo vendedores contra fraudes, mas mantendo a possibilidade de soluções para disputas legítimas.
Neste documento, apresentamos o Bitcoin, que resolve o problema do gasto duplo usando uma rede descentralizada. Essa rede cria um registro público e protegido por cálculos matemáticos, que garante a ordem das transações. Enquanto a maior parte da rede for controlada por pessoas honestas, o sistema será seguro contra ataques.
2. Transações
Para entender como funciona o Bitcoin, é importante saber como as transações são realizadas. Imagine que você quer transferir uma "moeda digital" para outra pessoa. No sistema do Bitcoin, essa "moeda" é representada por uma sequência de registros que mostram quem é o atual dono. Para transferi-la, você adiciona um novo registro comprovando que agora ela pertence ao próximo dono. Esse registro é protegido por um tipo especial de assinatura digital.
O que é uma assinatura digital?
Uma assinatura digital é como uma senha secreta, mas muito mais segura. No Bitcoin, cada usuário tem duas chaves: uma "chave privada", que é secreta e serve para criar a assinatura, e uma "chave pública", que pode ser compartilhada com todos e é usada para verificar se a assinatura é válida. Quando você transfere uma moeda, usa sua chave privada para assinar a transação, provando que você é o dono. A próxima pessoa pode usar sua chave pública para confirmar isso.
Como funciona na prática?
Cada "moeda" no Bitcoin é, na verdade, uma cadeia de assinaturas digitais. Vamos imaginar o seguinte cenário:
- A moeda está com o Dono 0 (você). Para transferi-la ao Dono 1, você assina digitalmente a transação com sua chave privada. Essa assinatura inclui o código da transação anterior (chamado de "hash") e a chave pública do Dono 1.
- Quando o Dono 1 quiser transferir a moeda ao Dono 2, ele assinará a transação seguinte com sua própria chave privada, incluindo também o hash da transação anterior e a chave pública do Dono 2.
- Esse processo continua, formando uma "cadeia" de transações. Qualquer pessoa pode verificar essa cadeia para confirmar quem é o atual dono da moeda.
Resolvendo o problema do gasto duplo
Um grande desafio com moedas digitais é o "gasto duplo", que é quando uma mesma moeda é usada em mais de uma transação. Para evitar isso, muitos sistemas antigos dependiam de uma entidade central confiável, como uma casa da moeda, que verificava todas as transações. No entanto, isso criava um ponto único de falha e centralizava o controle do dinheiro.
O Bitcoin resolve esse problema de forma inovadora: ele usa uma rede descentralizada onde todos os participantes (os "nós") têm acesso a um registro completo de todas as transações. Cada nó verifica se as transações são válidas e se a moeda não foi gasta duas vezes. Quando a maioria dos nós concorda com a validade de uma transação, ela é registrada permanentemente na blockchain.
Por que isso é importante?
Essa solução elimina a necessidade de confiar em uma única entidade para gerenciar o dinheiro, permitindo que qualquer pessoa no mundo use o Bitcoin sem precisar de permissão de terceiros. Além disso, ela garante que o sistema seja seguro e resistente a fraudes.
3. Servidor Timestamp
Para assegurar que as transações sejam realizadas de forma segura e transparente, o sistema Bitcoin utiliza algo chamado de "servidor de registro de tempo" (timestamp). Esse servidor funciona como um registro público que organiza as transações em uma ordem específica.
Ele faz isso agrupando várias transações em blocos e criando um código único chamado "hash". Esse hash é como uma impressão digital que representa todo o conteúdo do bloco. O hash de cada bloco é amplamente divulgado, como se fosse publicado em um jornal ou em um fórum público.
Esse processo garante que cada bloco de transações tenha um registro de quando foi criado e que ele existia naquele momento. Além disso, cada novo bloco criado contém o hash do bloco anterior, formando uma cadeia contínua de blocos conectados — conhecida como blockchain.
Com isso, se alguém tentar alterar qualquer informação em um bloco anterior, o hash desse bloco mudará e não corresponderá ao hash armazenado no bloco seguinte. Essa característica torna a cadeia muito segura, pois qualquer tentativa de fraude seria imediatamente detectada.
O sistema de timestamps é essencial para provar a ordem cronológica das transações e garantir que cada uma delas seja única e autêntica. Dessa forma, ele reforça a segurança e a confiança na rede Bitcoin.
4. Prova-de-Trabalho
Para implementar o registro de tempo distribuído no sistema Bitcoin, utilizamos um mecanismo chamado prova-de-trabalho. Esse sistema é semelhante ao Hashcash, desenvolvido por Adam Back, e baseia-se na criação de um código único, o "hash", por meio de um processo computacionalmente exigente.
A prova-de-trabalho envolve encontrar um valor especial que, quando processado junto com as informações do bloco, gere um hash que comece com uma quantidade específica de zeros. Esse valor especial é chamado de "nonce". Encontrar o nonce correto exige um esforço significativo do computador, porque envolve tentativas repetidas até que a condição seja satisfeita.
Esse processo é importante porque torna extremamente difícil alterar qualquer informação registrada em um bloco. Se alguém tentar mudar algo em um bloco, seria necessário refazer o trabalho de computação não apenas para aquele bloco, mas também para todos os blocos que vêm depois dele. Isso garante a segurança e a imutabilidade da blockchain.
A prova-de-trabalho também resolve o problema de decidir qual cadeia de blocos é a válida quando há múltiplas cadeias competindo. A decisão é feita pela cadeia mais longa, pois ela representa o maior esforço computacional já realizado. Isso impede que qualquer indivíduo ou grupo controle a rede, desde que a maioria do poder de processamento seja mantida por participantes honestos.
Para garantir que o sistema permaneça eficiente e equilibrado, a dificuldade da prova-de-trabalho é ajustada automaticamente ao longo do tempo. Se novos blocos estiverem sendo gerados rapidamente, a dificuldade aumenta; se estiverem sendo gerados muito lentamente, a dificuldade diminui. Esse ajuste assegura que novos blocos sejam criados aproximadamente a cada 10 minutos, mantendo o sistema estável e funcional.
5. Rede
A rede Bitcoin é o coração do sistema e funciona de maneira distribuída, conectando vários participantes (ou nós) para garantir o registro e a validação das transações. Os passos para operar essa rede são:
-
Transmissão de Transações: Quando alguém realiza uma nova transação, ela é enviada para todos os nós da rede. Isso é feito para garantir que todos estejam cientes da operação e possam validá-la.
-
Coleta de Transações em Blocos: Cada nó agrupa as novas transações recebidas em um "bloco". Este bloco será preparado para ser adicionado à cadeia de blocos (a blockchain).
-
Prova-de-Trabalho: Os nós competem para resolver a prova-de-trabalho do bloco, utilizando poder computacional para encontrar um hash válido. Esse processo é como resolver um quebra-cabeça matemático difícil.
-
Envio do Bloco Resolvido: Quando um nó encontra a solução para o bloco (a prova-de-trabalho), ele compartilha esse bloco com todos os outros nós na rede.
-
Validação do Bloco: Cada nó verifica o bloco recebido para garantir que todas as transações nele contidas sejam válidas e que nenhuma moeda tenha sido gasta duas vezes. Apenas blocos válidos são aceitos.
-
Construção do Próximo Bloco: Os nós que aceitaram o bloco começam a trabalhar na criação do próximo bloco, utilizando o hash do bloco aceito como base (hash anterior). Isso mantém a continuidade da cadeia.
Resolução de Conflitos e Escolha da Cadeia Mais Longa
Os nós sempre priorizam a cadeia mais longa, pois ela representa o maior esforço computacional já realizado, garantindo maior segurança. Se dois blocos diferentes forem compartilhados simultaneamente, os nós trabalharão no primeiro bloco recebido, mas guardarão o outro como uma alternativa. Caso o segundo bloco eventualmente forme uma cadeia mais longa (ou seja, tenha mais blocos subsequentes), os nós mudarão para essa nova cadeia.
Tolerância a Falhas
A rede é robusta e pode lidar com mensagens que não chegam a todos os nós. Uma transação não precisa alcançar todos os nós de imediato; basta que chegue a um número suficiente deles para ser incluída em um bloco. Da mesma forma, se um nó não receber um bloco em tempo hábil, ele pode solicitá-lo ao perceber que está faltando quando o próximo bloco é recebido.
Esse mecanismo descentralizado permite que a rede Bitcoin funcione de maneira segura, confiável e resiliente, sem depender de uma autoridade central.
6. Incentivo
O incentivo é um dos pilares fundamentais que sustenta o funcionamento da rede Bitcoin, garantindo que os participantes (nós) continuem operando de forma honesta e contribuindo com recursos computacionais. Ele é estruturado em duas partes principais: a recompensa por mineração e as taxas de transação.
Recompensa por Mineração
Por convenção, o primeiro registro em cada bloco é uma transação especial que cria novas moedas e as atribui ao criador do bloco. Essa recompensa incentiva os mineradores a dedicarem poder computacional para apoiar a rede. Como não há uma autoridade central para emitir moedas, essa é a maneira pela qual novas moedas entram em circulação. Esse processo pode ser comparado ao trabalho de garimpeiros, que utilizam recursos para colocar mais ouro em circulação. No caso do Bitcoin, o "recurso" consiste no tempo de CPU e na energia elétrica consumida para resolver a prova-de-trabalho.
Taxas de Transação
Além da recompensa por mineração, os mineradores também podem ser incentivados pelas taxas de transação. Se uma transação utiliza menos valor de saída do que o valor de entrada, a diferença é tratada como uma taxa, que é adicionada à recompensa do bloco contendo essa transação. Com o passar do tempo e à medida que o número de moedas em circulação atinge o limite predeterminado, essas taxas de transação se tornam a principal fonte de incentivo, substituindo gradualmente a emissão de novas moedas. Isso permite que o sistema opere sem inflação, uma vez que o número total de moedas permanece fixo.
Incentivo à Honestidade
O design do incentivo também busca garantir que os participantes da rede mantenham um comportamento honesto. Para um atacante que consiga reunir mais poder computacional do que o restante da rede, ele enfrentaria duas escolhas:
- Usar esse poder para fraudar o sistema, como reverter transações e roubar pagamentos.
- Seguir as regras do sistema, criando novos blocos e recebendo recompensas legítimas.
A lógica econômica favorece a segunda opção, pois um comportamento desonesto prejudicaria a confiança no sistema, diminuindo o valor de todas as moedas, incluindo aquelas que o próprio atacante possui. Jogar dentro das regras não apenas maximiza o retorno financeiro, mas também preserva a validade e a integridade do sistema.
Esse mecanismo garante que os incentivos econômicos estejam alinhados com o objetivo de manter a rede segura, descentralizada e funcional ao longo do tempo.
7. Recuperação do Espaço em Disco
Depois que uma moeda passa a estar protegida por muitos blocos na cadeia, as informações sobre as transações antigas que a geraram podem ser descartadas para economizar espaço em disco. Para que isso seja possível sem comprometer a segurança, as transações são organizadas em uma estrutura chamada "árvore de Merkle". Essa árvore funciona como um resumo das transações: em vez de armazenar todas elas, guarda apenas um "hash raiz", que é como uma assinatura compacta que representa todo o grupo de transações.
Os blocos antigos podem, então, ser simplificados, removendo as partes desnecessárias dessa árvore. Apenas a raiz do hash precisa ser mantida no cabeçalho do bloco, garantindo que a integridade dos dados seja preservada, mesmo que detalhes específicos sejam descartados.
Para exemplificar: imagine que você tenha vários recibos de compra. Em vez de guardar todos os recibos, você cria um documento e lista apenas o valor total de cada um. Mesmo que os recibos originais sejam descartados, ainda é possível verificar a soma com base nos valores armazenados.
Além disso, o espaço ocupado pelos blocos em si é muito pequeno. Cada bloco sem transações ocupa apenas cerca de 80 bytes. Isso significa que, mesmo com blocos sendo gerados a cada 10 minutos, o crescimento anual em espaço necessário é insignificante: apenas 4,2 MB por ano. Com a capacidade de armazenamento dos computadores crescendo a cada ano, esse espaço continuará sendo trivial, garantindo que a rede possa operar de forma eficiente sem problemas de armazenamento, mesmo a longo prazo.
8. Verificação de Pagamento Simplificada
É possível confirmar pagamentos sem a necessidade de operar um nó completo da rede. Para isso, o usuário precisa apenas de uma cópia dos cabeçalhos dos blocos da cadeia mais longa (ou seja, a cadeia com maior esforço de trabalho acumulado). Ele pode verificar a validade de uma transação ao consultar os nós da rede até obter a confirmação de que tem a cadeia mais longa. Para isso, utiliza-se o ramo Merkle, que conecta a transação ao bloco em que ela foi registrada.
Entretanto, o método simplificado possui limitações: ele não pode confirmar uma transação isoladamente, mas sim assegurar que ela ocupa um lugar específico na cadeia mais longa. Dessa forma, se um nó da rede aprova a transação, os blocos subsequentes reforçam essa aceitação.
A verificação simplificada é confiável enquanto a maioria dos nós da rede for honesta. Contudo, ela se torna vulnerável caso a rede seja dominada por um invasor. Nesse cenário, um atacante poderia fabricar transações fraudulentas que enganariam o usuário temporariamente até que o invasor obtivesse controle completo da rede.
Uma estratégia para mitigar esse risco é configurar alertas nos softwares de nós completos. Esses alertas identificam blocos inválidos, sugerindo ao usuário baixar o bloco completo para confirmar qualquer inconsistência. Para maior segurança, empresas que realizam pagamentos frequentes podem preferir operar seus próprios nós, reduzindo riscos e permitindo uma verificação mais direta e confiável.
9. Combinando e Dividindo Valor
No sistema Bitcoin, cada unidade de valor é tratada como uma "moeda" individual, mas gerenciar cada centavo como uma transação separada seria impraticável. Para resolver isso, o Bitcoin permite que valores sejam combinados ou divididos em transações, facilitando pagamentos de qualquer valor.
Entradas e Saídas
Cada transação no Bitcoin é composta por:
- Entradas: Representam os valores recebidos em transações anteriores.
- Saídas: Correspondem aos valores enviados, divididos entre os destinatários e, eventualmente, o troco para o remetente.
Normalmente, uma transação contém:
- Uma única entrada com valor suficiente para cobrir o pagamento.
- Ou várias entradas combinadas para atingir o valor necessário.
O valor total das saídas nunca excede o das entradas, e a diferença (se houver) pode ser retornada ao remetente como troco.
Exemplo Prático
Imagine que você tem duas entradas:
- 0,03 BTC
- 0,07 BTC
Se deseja enviar 0,08 BTC para alguém, a transação terá:
- Entrada: As duas entradas combinadas (0,03 + 0,07 BTC = 0,10 BTC).
- Saídas: Uma para o destinatário (0,08 BTC) e outra como troco para você (0,02 BTC).
Essa flexibilidade permite que o sistema funcione sem precisar manipular cada unidade mínima individualmente.
Difusão e Simplificação
A difusão de transações, onde uma depende de várias anteriores e assim por diante, não representa um problema. Não é necessário armazenar ou verificar o histórico completo de uma transação para utilizá-la, já que o registro na blockchain garante sua integridade.
10. Privacidade
O modelo bancário tradicional oferece um certo nível de privacidade, limitando o acesso às informações financeiras apenas às partes envolvidas e a um terceiro confiável (como bancos ou instituições financeiras). No entanto, o Bitcoin opera de forma diferente, pois todas as transações são publicamente registradas na blockchain. Apesar disso, a privacidade pode ser mantida utilizando chaves públicas anônimas, que desvinculam diretamente as transações das identidades das partes envolvidas.
Fluxo de Informação
- No modelo tradicional, as transações passam por um terceiro confiável que conhece tanto o remetente quanto o destinatário.
- No Bitcoin, as transações são anunciadas publicamente, mas sem revelar diretamente as identidades das partes. Isso é comparável a dados divulgados por bolsas de valores, onde informações como o tempo e o tamanho das negociações (a "fita") são públicas, mas as identidades das partes não.
Protegendo a Privacidade
Para aumentar a privacidade no Bitcoin, são adotadas as seguintes práticas:
- Chaves Públicas Anônimas: Cada transação utiliza um par de chaves diferentes, dificultando a associação com um proprietário único.
- Prevenção de Ligação: Ao usar chaves novas para cada transação, reduz-se a possibilidade de links evidentes entre múltiplas transações realizadas pelo mesmo usuário.
Riscos de Ligação
Embora a privacidade seja fortalecida, alguns riscos permanecem:
- Transações multi-entrada podem revelar que todas as entradas pertencem ao mesmo proprietário, caso sejam necessárias para somar o valor total.
- O proprietário da chave pode ser identificado indiretamente por transações anteriores que estejam conectadas.
11. Cálculos
Imagine que temos um sistema onde as pessoas (ou computadores) competem para adicionar informações novas (blocos) a um grande registro público (a cadeia de blocos ou blockchain). Este registro é como um livro contábil compartilhado, onde todos podem verificar o que está escrito.
Agora, vamos pensar em um cenário: um atacante quer enganar o sistema. Ele quer mudar informações já registradas para beneficiar a si mesmo, por exemplo, desfazendo um pagamento que já fez. Para isso, ele precisa criar uma versão alternativa do livro contábil (a cadeia de blocos dele) e convencer todos os outros participantes de que essa versão é a verdadeira.
Mas isso é extremamente difícil.
Como o Ataque Funciona
Quando um novo bloco é adicionado à cadeia, ele depende de cálculos complexos que levam tempo e esforço. Esses cálculos são como um grande quebra-cabeça que precisa ser resolvido.
- Os “bons jogadores” (nós honestos) estão sempre trabalhando juntos para resolver esses quebra-cabeças e adicionar novos blocos à cadeia verdadeira.
- O atacante, por outro lado, precisa resolver quebra-cabeças sozinho, tentando “alcançar” a cadeia honesta para que sua versão alternativa pareça válida.
Se a cadeia honesta já está vários blocos à frente, o atacante começa em desvantagem, e o sistema está projetado para que a dificuldade de alcançá-los aumente rapidamente.
A Corrida Entre Cadeias
Você pode imaginar isso como uma corrida. A cada bloco novo que os jogadores honestos adicionam à cadeia verdadeira, eles se distanciam mais do atacante. Para vencer, o atacante teria que resolver os quebra-cabeças mais rápido que todos os outros jogadores honestos juntos.
Suponha que:
- A rede honesta tem 80% do poder computacional (ou seja, resolve 8 de cada 10 quebra-cabeças).
- O atacante tem 20% do poder computacional (ou seja, resolve 2 de cada 10 quebra-cabeças).
Cada vez que a rede honesta adiciona um bloco, o atacante tem que "correr atrás" e resolver mais quebra-cabeças para alcançar.
Por Que o Ataque Fica Cada Vez Mais Improvável?
Vamos usar uma fórmula simples para mostrar como as chances de sucesso do atacante diminuem conforme ele precisa "alcançar" mais blocos:
P = (q/p)^z
- q é o poder computacional do atacante (20%, ou 0,2).
- p é o poder computacional da rede honesta (80%, ou 0,8).
- z é a diferença de blocos entre a cadeia honesta e a cadeia do atacante.
Se o atacante está 5 blocos atrás (z = 5):
P = (0,2 / 0,8)^5 = (0,25)^5 = 0,00098, (ou, 0,098%)
Isso significa que o atacante tem menos de 0,1% de chance de sucesso — ou seja, é muito improvável.
Se ele estiver 10 blocos atrás (z = 10):
P = (0,2 / 0,8)^10 = (0,25)^10 = 0,000000095, (ou, 0,0000095%).
Neste caso, as chances de sucesso são praticamente nulas.
Um Exemplo Simples
Se você jogar uma moeda, a chance de cair “cara” é de 50%. Mas se precisar de 10 caras seguidas, sua chance já é bem menor. Se precisar de 20 caras seguidas, é quase impossível.
No caso do Bitcoin, o atacante precisa de muito mais do que 20 caras seguidas. Ele precisa resolver quebra-cabeças extremamente difíceis e alcançar os jogadores honestos que estão sempre à frente. Isso faz com que o ataque seja inviável na prática.
Por Que Tudo Isso é Seguro?
- A probabilidade de sucesso do atacante diminui exponencialmente. Isso significa que, quanto mais tempo passa, menor é a chance de ele conseguir enganar o sistema.
- A cadeia verdadeira (honesta) está protegida pela força da rede. Cada novo bloco que os jogadores honestos adicionam à cadeia torna mais difícil para o atacante alcançar.
E Se o Atacante Tentar Continuar?
O atacante poderia continuar tentando indefinidamente, mas ele estaria gastando muito tempo e energia sem conseguir nada. Enquanto isso, os jogadores honestos estão sempre adicionando novos blocos, tornando o trabalho do atacante ainda mais inútil.
Assim, o sistema garante que a cadeia verdadeira seja extremamente segura e que ataques sejam, na prática, impossíveis de ter sucesso.
12. Conclusão
Propusemos um sistema de transações eletrônicas que elimina a necessidade de confiança, baseando-se em assinaturas digitais e em uma rede peer-to-peer que utiliza prova de trabalho. Isso resolve o problema do gasto duplo, criando um histórico público de transações imutável, desde que a maioria do poder computacional permaneça sob controle dos participantes honestos. A rede funciona de forma simples e descentralizada, com nós independentes que não precisam de identificação ou coordenação direta. Eles entram e saem livremente, aceitando a cadeia de prova de trabalho como registro do que ocorreu durante sua ausência. As decisões são tomadas por meio do poder de CPU, validando blocos legítimos, estendendo a cadeia e rejeitando os inválidos. Com este mecanismo de consenso, todas as regras e incentivos necessários para o funcionamento seguro e eficiente do sistema são garantidos.
Faça o download do whitepaper original em português: https://bitcoin.org/files/bitcoin-paper/bitcoin_pt_br.pdf
-
 @ f9cf4e94:96abc355
2025-01-18 06:09:50
@ f9cf4e94:96abc355
2025-01-18 06:09:50Para esse exemplo iremos usar: | Nome | Imagem | Descrição | | --------------- | ------------------------------------------------------------ | ------------------------------------------------------------ | | Raspberry PI B+ |
 | Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |
| Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |  | 16Gb |
| 16Gb |Recomendo que use o Ubuntu Server para essa instalação. Você pode baixar o Ubuntu para Raspberry Pi aqui. O passo a passo para a instalação do Ubuntu no Raspberry Pi está disponível aqui. Não instale um desktop (como xubuntu, lubuntu, xfce, etc.).
Passo 1: Atualizar o Sistema 🖥️
Primeiro, atualize seu sistema e instale o Tor:
bash apt update apt install tor
Passo 2: Criar o Arquivo de Serviço
nrs.service🔧Crie o arquivo de serviço que vai gerenciar o servidor Nostr. Você pode fazer isso com o seguinte conteúdo:
```unit [Unit] Description=Nostr Relay Server Service After=network.target
[Service] Type=simple WorkingDirectory=/opt/nrs ExecStart=/opt/nrs/nrs-arm64 Restart=on-failure
[Install] WantedBy=multi-user.target ```
Passo 3: Baixar o Binário do Nostr 🚀
Baixe o binário mais recente do Nostr aqui no GitHub.
Passo 4: Criar as Pastas Necessárias 📂
Agora, crie as pastas para o aplicativo e o pendrive:
bash mkdir -p /opt/nrs /mnt/edriver
Passo 5: Listar os Dispositivos Conectados 🔌
Para saber qual dispositivo você vai usar, liste todos os dispositivos conectados:
bash lsblk
Passo 6: Formatando o Pendrive 💾
Escolha o pendrive correto (por exemplo,
/dev/sda) e formate-o:bash mkfs.vfat /dev/sda
Passo 7: Montar o Pendrive 💻
Monte o pendrive na pasta
/mnt/edriver:bash mount /dev/sda /mnt/edriver
Passo 8: Verificar UUID dos Dispositivos 📋
Para garantir que o sistema monte o pendrive automaticamente, liste os UUID dos dispositivos conectados:
bash blkid
Passo 9: Alterar o
fstabpara Montar o Pendrive Automáticamente 📝Abra o arquivo
/etc/fstabe adicione uma linha para o pendrive, com o UUID que você obteve no passo anterior. A linha deve ficar assim:fstab UUID=9c9008f8-f852 /mnt/edriver vfat defaults 0 0
Passo 10: Copiar o Binário para a Pasta Correta 📥
Agora, copie o binário baixado para a pasta
/opt/nrs:bash cp nrs-arm64 /opt/nrs
Passo 11: Criar o Arquivo de Configuração 🛠️
Crie o arquivo de configuração com o seguinte conteúdo e salve-o em
/opt/nrs/config.yaml:yaml app_env: production info: name: Nostr Relay Server description: Nostr Relay Server pub_key: "" contact: "" url: http://localhost:3334 icon: https://external-content.duckduckgo.com/iu/?u= https://public.bnbstatic.com/image/cms/crawler/COINCU_NEWS/image-495-1024x569.png base_path: /mnt/edriver negentropy: true
Passo 12: Copiar o Serviço para o Diretório de Systemd ⚙️
Agora, copie o arquivo
nrs.servicepara o diretório/etc/systemd/system/:bash cp nrs.service /etc/systemd/system/Recarregue os serviços e inicie o serviço
nrs:bash systemctl daemon-reload systemctl enable --now nrs.service
Passo 13: Configurar o Tor 🌐
Abra o arquivo de configuração do Tor
/var/lib/tor/torrce adicione a seguinte linha:torrc HiddenServiceDir /var/lib/tor/nostr_server/ HiddenServicePort 80 127.0.0.1:3334
Passo 14: Habilitar e Iniciar o Tor 🧅
Agora, ative e inicie o serviço Tor:
bash systemctl enable --now tor.serviceO Tor irá gerar um endereço
.onionpara o seu servidor Nostr. Você pode encontrá-lo no arquivo/var/lib/tor/nostr_server/hostname.
Observações ⚠️
- Com essa configuração, os dados serão salvos no pendrive, enquanto o binário ficará no cartão SD do Raspberry Pi.
- O endereço
.oniondo seu servidor Nostr será algo como:ws://y3t5t5wgwjif<exemplo>h42zy7ih6iwbyd.onion.
Agora, seu servidor Nostr deve estar configurado e funcionando com Tor! 🥳
Se este artigo e as informações aqui contidas forem úteis para você, convidamos a considerar uma doação ao autor como forma de reconhecimento e incentivo à produção de novos conteúdos.
-
 @ a5142938:0ef19da3
2025-06-04 08:00:22
@ a5142938:0ef19da3
2025-06-04 08:00:22Brands
Cosilana is a German brand that creates clothing exclusively from organic cotton, silk, and wool for women, babies, and children.
Natural materials used in products
Categories of products offered
This brand offers products made entirely from natural materials in the following categories:
#Clothing
- Clothing fits : babies, children, women
- Underwear : panties
- One piece : bodysuits, jumpsuits
- Tops : jackets, sweaters, t-shirts, tank tops
- Bottoms : leggings, pants-trousers, shorts
- Head & handwear : gloves, hats
- Nightwear : pyjamas
#Home
- Linen : blankets, sleeping bags
Other information
- GOTS certification
- Made in Germany
- Made in Europe
- Non mulesed wool and animal welfare declaration
👉 Learn more on the brand website
Where to find their products?
- Le mouton à lunettes (in French, shipping area: France, Belgium, Luxemburg)
- Mama Owl (shipping area: UK and international)
- Chouchous (in French, shipping area: France and international)
📝 You can contribute to this entry by suggesting edits in comments.
🗣️ Do you use this brand's products? Share your opinion in the comments.
⚡ Happy to have found this information? Support the project by making a donation to thank the contributors.
-
 @ 4fa5d1c4:fd6c6e41
2025-06-04 17:45:05
@ 4fa5d1c4:fd6c6e41
2025-06-04 17:45:051. Einleitung
Dieser Beitrag bietet eine detaillierte Einführung in Nostr - ein dezentrales Protokoll für soziale Medien, das sich grundlegend von traditionellen und föderierten Plattformen unterscheidet - und erweitert seine Diskussion, um das Potenzial für die Integration von Nostr in die Entwicklung von Bildungsplattformen im Sinne von Open Educational Practices (OEP) zu untersuchen. Nostr ist als leichtgewichtiger, zensurresistenter Mechanismus konzipiert, der in erster Linie auf einer kryptografischen Schlüsselverwaltung und einer Client-zentrierten Architektur basiert, die zusammen eine dezentrale Identitätskontrolle und Autonomie über digitale Inhalte ermöglichen. Im Gegensatz zu konventionellen zentralisierten Modellen, die sich auf servergestützte Kontrolle oder föderierte Systeme wie Mastodon, die Moderation und Identitätsspeicherung zusammenfassen, stützt sich Nostr auf ein Netzwerk von "Relais", die ohne direkte Interkommunikation arbeiten, wobei alle Funktionen der Datenaggregation, des Austauschs von Inhalten zwischen den Räumen und der Benutzerinteraktion an die Client-Anwendungen delegiert werden. Ziel dieses Beitrags ist es daher, einen umfassenden technischen und konzeptionellen Überblick über die Architektur des Protokolls und eine kritische Diskussion seiner Anwendbarkeit im Kontext dezentraler Bildungsplattformen zu geben, die eine offene, nutzergesteuerte Erstellung, Verwaltung und Verteilung von Inhalten fördern und damit den Prinzipien des OEP entsprechen.
2. Hintergrund und Motivation
Die Entwicklung der sozialen Medien in den letzten zwei Jahrzehnten war geprägt von zunehmend zentralisierten Plattformen, die sowohl die digitale Identität der Nutzer als auch die von ihnen erstellten Inhalte kontrollieren, was oft zu Zensur, algorithmischer Manipulation und Einzelausfällen führt. Im Gegensatz dazu haben sich dezentralisierte Social-Media-Protokolle wie Nostr als innovative Antwort auf diese Zentralisierungsfallen entwickelt, die offene, kryptografisch sichere und verteilte Architekturen verwenden. Nostr wurde mit dem ausdrücklichen Schwerpunkt konzipiert, den Nutzern die volle Kontrolle über ihre Kontoauthentifizierung und digitale Identität zu geben, was durch die Verwaltung von kryptografischen Schlüsselpaaren analog zu denen in Bitcoin-Wallets erreicht wird. Dieses Modell verbessert nicht nur die zensurresistenten Eigenschaften der Plattform, sondern verändert auch grundlegend die Machtdynamik in traditionellen sozialen Netzwerken, da es die Abhängigkeit von zentralen Behörden minimiert und die Möglichkeiten der Ausbeutung und Überwachung verringert. Im Kontext von Bildungsökosystemen bieten diese Merkmale eine solide Grundlage für die Entwicklung von Plattformen, die transparent, partizipatorisch und widerstandsfähig sind, da sie die gemeinsame Nutzung und kontinuierliche Weiterentwicklung von Bildungsressourcen ohne zentralisierte Kontrolle oder Unternehmenssteuerung unterstützen.
3. Technische Architektur von Nostr
Die Architektur von Nostr basiert in erster Linie auf zwei integralen Komponenten: Clients und Relays. Clients sind die benutzerseitigen Anwendungen, die die Erstellung, Veröffentlichung und Aggregation von Inhalten ermöglichen, während Relays Server sind, die von den Benutzern generierte Nachrichten, so genannte "Events", empfangen, speichern und weiterleiten. Eine der wichtigsten Neuerungen des Nostr-Protokolls ist die radikale Entkopplung der traditionellen Client-Server-Beziehung: Die Relais müssen sich nicht synchronisieren oder miteinander kommunizieren, was bedeutet, dass die Replikation von Inhalten und die Aggregation von Daten zwischen den Räumen vollständig auf der Client-Seite stattfindet. Dies minimiert die zentrale Kontrolle und schafft ein verteiltes, relaisbasiertes System, das von Natur aus resistent gegen Zensur ist, da die Dichte der verfügbaren Relays und die Möglichkeit der Nutzer, sich mit mehreren Relays zu verbinden, sicherstellen, dass die Inhalte auch dann zugänglich bleiben, wenn bestimmte Relays ausfallen oder kompromittiert sind.
In Nostr sind Ereignisse als JSON-Objekte strukturiert, die einem definierten Schema mit verschiedenen "Arten" (NIPs) entsprechen, um spezifische Funktionalitäten und andere zukünftige Erweiterungen zu unterstützen. Jedes Ereignis wird mit dem privaten kryptografischen Schlüssel des Nutzers digital signiert, was die Authentizität und Integrität der Daten garantiert und gleichzeitig eine sichere, pseudonyme Interaktion ermöglicht. Da innerhalb des Protokolls keine zentrale Behörde oder ein einziger Identitätsspeicher existiert, behalten die Nutzer die vollständige Kontrolle über ihre digitalen Identitäten, und wenn der private Schlüssel verloren geht, ist das entsprechende Konto unwiederbringlich. Dieser Ansatz verankert den Grundsatz, dass Identität sowohl dezentralisiert als auch unveränderlich ist, und stärkt die individuelle Kontrolle über persönliche Daten und Inhalte.
Da die Relays unabhängig voneinander von verschiedenen Betreibern verwaltet und nicht von zentralen Diensten koordiniert werden, können die Benutzer mehrere Relays auswählen, um die Bereitstellung und Replikation von Inhalten zu optimieren. Diese architektonische Entscheidung verbessert die Redundanz und Ausfallsicherheit erheblich, bringt aber gleichzeitig technische Herausforderungen in Bezug auf Standardisierung, Moderation und effiziente Kommunikation zwischen den Clients mit sich. Nostr integriert auch Bitcoin-basierte Mikrozahlungen (bekannt als "Zaps"), um finanzielle Anreize für den Betrieb von Relay-Servern zu schaffen und so die Herausforderungen der wirtschaftlichen Nachhaltigkeit in einer dezentralen Infrastruktur zu bewältigen. Die Design-Entscheidungen in Nostr fördern Offenheit und Innovation, indem sie es jeder Person oder Organisation mit ausreichenden technischen Fähigkeiten erlauben, ein Relay zu hosten oder einen Client zu entwickeln, was zu einem lebendigen Ökosystem von verschiedenen Anwendungen und Diensten führt.
4. Identitätsmanagement und Moderation
Im Mittelpunkt des dezentralen Paradigmas von Nostr steht der Ansatz der Identitätsverwaltung, der sich von traditionellen Systemen unterscheidet, bei denen Identitäten als Kontodaten von zentralen Servern verwaltet werden. Bei Nostr verfügt jeder Benutzer über ein einzigartiges kryptografisches Schlüsselpaar, wobei der öffentliche Schlüssel als dauerhafte digitale Kennung und der private Schlüssel als Mittel zum Signieren aller Aktionen und Ereignisse dient. Dieses kryptonative Modell gewährleistet nicht nur robuste Sicherheit und Authentizität, sondern überlässt den Nutzern auch die alleinige Verantwortung für die Verwaltung ihrer Schlüssel - was sowohl die Freiheit als auch das Risiko eines vollständig dezentralen Identitätssystems unterstreicht.Dieses empfindliche Gleichgewicht unterstreicht die Autonomie der Nutzer und steht im Einklang mit dem breiteren Ethos dezentraler sozialer Medien, in denen keine einzelne Instanz die Identität einer Person ohne Zugang zu ihrem privaten Schlüssel außer Kraft setzen oder manipulieren kann.
Die Moderation in Nostr ist aufgrund des dezentralen Kuratierungsmodells noch komplexer. Die Inhalte werden nicht von einer zentralen Behörde moderiert, sondern durch eine Kombination aus relaisspezifischen Richtlinien und clientseitigen Kontrollen, wie z. B. benutzerdefinierte Listen für persönliche Kuratoren oder Sperr-/Stummschaltungsfunktionen. Dieser Ansatz fördert zwar die freie Meinungsäußerung und unterstützt eine Vielzahl von Standpunkten, kann aber auch zu uneinheitlichen Moderationsrichtlinien und fragmentierten Nutzererfahrungen auf verschiedenen Relays und Clients führen, was für die Nutzer eine erhebliche technische und verhaltensbezogene Belastung darstellt, wenn sie ihre digitalen Umgebungen kuratieren wollen.
5. Skalierbarkeit und Widerstandsfähigkeit gegen Zensur
Ein entscheidendes Merkmal des Nostr-Protokolls ist sein hohes Maß an Skalierbarkeit und Zensurresistenz, das durch seine verteilte, relaisbasierte Architektur erreicht wird. Durch die Dezentralisierung der Speicherung und Verbreitung von Inhalten auf zahlreiche unabhängige Relays entschärft Nostr die üblichen Schwachstellen zentralisierter sozialer Plattformen, wie z. B. Single Points of Failure oder das Potenzial für staatliche oder unternehmensgesteuerte Zensur. Mehrere Relays können gleichzeitig arbeiten, wodurch sichergestellt wird, dass die Stabilität des Netzwerks auch dann erhalten bleibt, wenn einige von ihnen vom Netz genommen werden oder behördlichem Druck ausgesetzt sind, und dass Inhalte für Kunden, die mit alternativen Relays verbunden sind, zugänglich bleiben.
Die Skalierbarkeit von Nostr wird dadurch verbessert, dass sich die Nutzenden gleichzeitig mit mehreren Relays verbinden können, was die Replikation von Inhalten über ein globales Netz von Servern ermöglicht, das sich über zahlreiche geografische Regionen und autonome Systeme erstreckt. Dieser Replikationsmechanismus bringt jedoch Herausforderungen mit sich, wie z. B. eine erhöhte Redundanz bei der Speicher- und Bandbreitennutzung, die eine sorgfältige Optimierung und die Entwicklung innovativer clientseitiger Strategien erfordern, um den Datenabruf zu verwalten und den Overhead zu reduzieren, ohne die Verfügbarkeit zu beeinträchtigen. Darüber hinaus trägt die Dezentralisierung der Zuständigkeiten für Kuratierung und Moderation zu einer dynamischen Umgebung bei, in der Inhalte sowohl gegen erzwungene Löschungen resistent als auch an die Bedürfnisse der Nutzer anpassbar sind, wenn auch auf Kosten von Einheitlichkeit und vorhersehbarer Nutzererfahrung.
6. Vergleich mit föderierten und zentralisierten Modellen
Das Aufkommen dezentraler Protokolle wie Nostr steht in scharfem Kontrast zu föderierten Netzwerken wie Mastodon, die das ActivityPub-Protokoll verwenden. Während föderierte Systeme die Kontrolle über unabhängige Instanzen verteilen, verlassen sie sich immer noch auf ein gewisses Maß an Zentralisierung auf der Ebene jeder einzelnen Instanz, von denen jede ihre eigenen Richtlinien bezüglich Moderation, Identitätsüberprüfung und Inhaltszensur durchsetzt. In diesen Systemen ist die Verwaltung zwar auf mehrere Knotenpunkte verteilt, aber es besteht eine Abhängigkeit von Serveradministratoren, die erhebliche Macht über den Inhalt und die Identität der Benutzer haben; dies steht im Gegensatz zu Nostrs vollständig kundenorientiertem Kurations- und Identitätsverwaltungsmodell, das darauf abzielt, jeden einzelnen Kontrollpunkt zu eliminieren.
In zentralisierten Architekturen werden Benutzerdaten und -identitäten auf proprietäre und undurchsichtige Weise verwaltet, wodurch Inhalte den Launen von Unternehmensrichtlinien und externem Druck ausgesetzt werden, was zu Überwachung, gezielter Zensur oder einseitiger algorithmischer Manipulation von Inhalten führen kann. Das Design von Nostr - das auf kryptografischer Authentifizierung, clientseitiger Datenaggregation und dem erlaubnisfreien Betrieb von Relay-Servern beruht - stellt eine radikale Abkehr dar, die das Gleichgewicht der Macht fest in die Hände der einzelnen Nutzer und nicht in die Hände zentraler Behörden legt.
7. Implikationen für Bildungsplattformen
Das Potenzial für die Integration des dezentralen Protokolls von Nostr in Bildungsplattformen bietet eine transformative Gelegenheit zur Unterstützung von Open Educational Practices (OEP). OEP legt den Schwerpunkt auf Inklusion, Autonomie der Lernenden, kollaborative Wissenserstellung und offenen Zugang zu Bildungsressourcen. Herkömmliche Bildungsplattformen sind oft durch zentralisierte Architekturen eingeschränkt, die den Zugang behindern und Innovationen unterdrücken können, da sie auf einzelne administrative Kontrollen und proprietäre Content-Management-Systeme angewiesen sind.
Durch die Nutzung der dezentralen Infrastruktur von Nostr können Bildungsplattformen aufgebaut werden, die es Lehrenden und Lernenden ermöglichen, die volle Kontrolle über ihre digitalen Identitäten und Bildungsinhalte zu behalten, ohne das Risiko von Zensur oder externer Einmischung. In solchen Systemen verwaltet jeder Teilnehmer seine eigene Identität mithilfe von kryptografischen Schlüsseln, wodurch sichergestellt wird, dass Bildungsleistungen, Beiträge und Zeugnisse auf überprüfbare und unveränderliche Weise aufgezeichnet werden. Dies fördert ein Umfeld, in dem die Schaffung und Verbreitung von Wissen wirklich von den Teilnehmern selbst bestimmt wird, frei von den Zwängen, die von zentralen Torwächtern auferlegt werden.
Darüber hinaus bietet die relaisbasierte Architektur von Nostr eine beispiellose Skalierbarkeit und Ausfallsicherheit - Eigenschaften, die für ein Bildungsökosystem, das eine Vielzahl von Nutzern mit unterschiedlichem geografischen und sozioökonomischen Hintergrund unterstützen muss, unerlässlich sind. Bildungsinhalte - von digitalen Lehrbüchern und Multimedia-Vorlesungen bis hin zu interaktiven Diskursen und gemeinschaftlichen Projekten - können gespeichert und über mehrere Relays repliziert werden, um sicherzustellen, dass der Zugang auch bei lokalen Netzwerkausfällen oder Zensurversuchen erhalten bleibt.
Das offene Protokoll von Nostr ist außerdem eine ideale Grundlage für die Entwicklung interoperabler Bildungsplattformen, auf denen Drittentwickler und Bildungseinrichtungen maßgeschneiderte Clients und Anwendungen für pädagogische Zwecke erstellen können. Dieser Ansatz fördert ein vielfältiges Ökosystem von Bildungswerkzeugen und -diensten, die nahtlos zusammenarbeiten, ohne auf eine einzige proprietäre Plattform beschränkt zu sein, und steht damit im Einklang mit dem Ethos des OEP. Pädagogen können digitale Lernumgebungen entwerfen, die die kollaborative Erstellung von Inhalten, Peer-Reviews und Community-gesteuerte Kuration unterstützen und gleichzeitig von der Sicherheit und Transparenz profitieren, die das kryptografische Grundgerüst von Nostr bietet.
Darüber hinaus gewährleistet die inhärente Zensurresistenz von Nostr, dass Bildungsinhalte zugänglich und frei von staatlichen oder unternehmerischen Eingriffen bleiben - ein besonders wichtiger Aspekt für Lernende in Regionen, in denen der Zugang zu Informationen eingeschränkt oder überwacht wird. Diese Widerstandsfähigkeit untermauert nicht nur die demokratische Verbreitung von Wissen, sondern unterstützt auch den Grundsatz eines digitalen Gemeinguts, bei dem Bildungsressourcen kollektiv verwaltet und gemeinsam genutzt werden. In diesem Zusammenhang kann Nostr genutzt werden, um Bildungsplattformen zu entwickeln, die nicht nur robust und integrativ sind, sondern auch auf die Bedürfnisse marginalisierter oder unterrepräsentierter Gemeinschaften abgestimmt sind.
Zusätzlich zu diesen strukturellen Vorteilen kann die finanzielle Nachhaltigkeit dezentraler Bildungsplattformen durch die Integration von auf Kryptowährungen basierenden Anreizmechanismen gestärkt werden - wie die Unterstützung von Nostr für Bitcoin Lightning "Zaps" zeigt. Diese Micropayment-Systeme eröffnen Möglichkeiten für neuartige Finanzierungsmodelle, die Pädagogen und Inhaltsersteller direkt belohnen und so die Abhängigkeit von werbebasierten Einnahmen oder zentralisierten Finanzierungsströmen verringern, die häufig die Integrität der Bildung gefährden. Solche wirtschaftlichen Anreize können auch den Betrieb und die Wartung von Relay-Servern unterstützen und so sicherstellen, dass die dezentrale Infrastruktur belastbar und kontinuierlich für Bildungszwecke verfügbar bleibt.
8. Möglichkeiten für kollaboratives und kultursensibles Lernen
Über die technische Stabilität und Skalierbarkeit hinaus bietet die dezentrale Natur von Nostr bedeutende Möglichkeiten zur Förderung von kollaborativem Lernen und kultursensibler Pädagogik. Dezentralisierte Bildungsplattformen, die auf Nostr aufbauen, können lokale Gemeinschaften in die Lage versetzen, Inhalte zu erstellen und zu kuratieren, die kontextuell relevant und kulturell angemessen sind - ein entscheidender Faktor bei der Förderung von Bildungsgerechtigkeit und Inklusivität. In Umgebungen, in denen Mainstream-Bildungstechnologien als von oben nach unten betrachtet werden und nicht mit lokalen Werten oder pädagogischen Ansätzen übereinstimmen, ermöglicht eine dezentralisierte Infrastruktur die Entwicklung maßgeschneiderter digitaler Lernumgebungen, die lokale Kulturen, Sprachen und Traditionen widerspiegeln.
Dieser gemeinschaftsorientierte Bildungsansatz fördert das Gefühl der Eigenverantwortung bei Lernenden und Lehrenden gleichermaßen und ermutigt zur gemeinschaftlichen Schaffung von Wissen, das unterschiedliche Erkenntnistheorien respektiert. So können Pädagogen beispielsweise dezentrale "Lernräume" einrichten, in denen Open-Source-Lernmaterialien, Werkzeuge für die digitale Kompetenz und innovative Lehrmethoden gemeinsam genutzt und durch partizipatives Engagement kontinuierlich weiterentwickelt werden. In einem solchen Modell verschwimmen die Grenzen zwischen Lernenden und Lehrenden, was einen fließenden Ideenaustausch und die gemeinsame Schaffung von Wissen ermöglicht, die im Mittelpunkt offener Bildungspraktiken stehen.
Darüber hinaus ermöglicht die Flexibilität der Client-zentrierten Architektur von Nostr die Entwicklung von spezialisierten Bildungsclients, die auf die jeweiligen Lernstile und Disziplinen zugeschnitten sind. Diese Clients könnten Funktionen wie erweiterte Such- und Filterfunktionen für Bildungsinhalte, integrierte Anmerkungswerkzeuge für die gemeinsame Bearbeitung von Dokumenten und interoperable Identitätsmanagementsysteme enthalten, die es den Lernenden ermöglichen, ihre Anmeldedaten nahtlos in verschiedene digitale Lernumgebungen zu übertragen. Solche Innovationen würden nicht nur die Rolle der Nutzerautonomie beim digitalen Lernen stärken, sondern auch die Entwicklung von Bildungsnetzwerken fördern, die belastbar und anpassungsfähig sind und auf die sich verändernden pädagogischen Herausforderungen reagieren können.
9. Herausforderungen und Abhilfestrategien
Trotz der vielversprechenden Möglichkeiten ist die Integration von Nostr in Bildungsplattformen nicht unproblematisch. Gerade die Funktionen, die den Nutzern mehr Möglichkeiten bieten - wie selbstverwaltete kryptografische Schlüssel und dezentralisierte Inhaltsmoderation - führen auch Komplexitäten ein, die die Benutzerfreundlichkeit und Zugänglichkeit behindern können, insbesondere für Personen ohne fortgeschrittene technische Kenntnisse. Die Schlüsselverwaltung stellt beispielsweise eine kritische Schwachstelle dar; der Verlust eines privaten Schlüssels führt unwiderruflich zum Verlust der Identität und des Zugriffs auf die eigenen digitalen Beiträge - ein Risiko, das durch solide Bildungsinitiativen und Mechanismen zur Unterstützung der Nutzer angegangen werden muss.
Die technische Kompetenz von Lehrenden und Lernenden ist in diesem Zusammenhang von größter Bedeutung und erfordert die Entwicklung umfassender Einführungsverfahren, benutzerfreundlicher Schnittstellen und Hilfsmittel, die kryptografische Konzepte entmystifizieren und die Interaktion mit dezentralen Netzwerken vereinfachen. Zu diesem Zweck könnte der Einsatz intuitiver Bildungsmodule, interaktiver Tutorials und von der Community geleiteter Schulungen technische Barrieren abbauen und gleichzeitig die Entwicklung digitaler Kompetenzen fördern, die für die Navigation in dezentralen Netzwerken unerlässlich sind. Darüber hinaus muss die Herausforderung einer inkonsistenten Moderation und fragmentierten Nutzererfahrung aufgrund der heterogenen Richtlinien unabhängiger Relais und Clients durch die Einrichtung von Community-Governance-Rahmenwerken und interoperablen Standards angegangen werden, die eine Grundlinie der Qualität und Sicherheit auf der gesamten Plattform gewährleisten.
Strategien zur Bewältigung des mit der Skalierbarkeit verbundenen Overheads - wie etwa die redundante Replikation von Beiträgen über eine übermäßige Anzahl von Relays - sollten sich auf die Implementierung clientseitiger Optimierungstechniken konzentrieren, die die Ineffizienz von Bandbreite und Speicherplatz verringern, ohne die Belastbarkeit und Zugänglichkeit des Netzwerks zu beeinträchtigen. Kontinuierliche Forschung und iterative Verfeinerung werden notwendig sein, um ein Gleichgewicht zwischen den Vorteilen der Dezentralisierung und der ihr innewohnenden betrieblichen Komplexität zu finden und sicherzustellen, dass auf Nostr basierende Bildungsplattformen sowohl robust als auch benutzerfreundlich bleiben können.
10. Zukünftige Richtungen und Forschungsmöglichkeiten
Die Einbindung von Nostr in Bildungsplattformen stellt ein fruchtbares Gebiet für Forschung und Entwicklung dar, das zahlreiche Möglichkeiten zur Erkundung bietet. Zukünftige Arbeiten könnten das Design interoperabler Bildungsrahmenwerke erforschen, die die dezentrale Architektur von Nostr mit aufkommenden Technologien wie künstlicher Intelligenz, Blockchain-basiertem Credentialing und fortschrittlichen kryptographischen Techniken integrieren, um die Sicherheit, Zugänglichkeit und Authentizität in digitalen Lernumgebungen weiter zu verbessern. Die Erforschung gemeinschaftsbasierter Governance-Modelle ist ebenfalls gerechtfertigt, da dezentrale Plattformen Mechanismen für die kollektive Entscheidungsfindung und Konfliktlösung erfordern, die mit den Grundsätzen einer offenen, partizipativen Bildung vereinbar sind.
Ein möglicher Weg ist die Entwicklung modularer, quelloffener Bildungs-Clients, die sich nahtlos mit verschiedenen Relais verbinden lassen und den Lehrkräften leistungsstarke Tools zur Kuratierung und Moderation von Inhalten bieten. Diese Clients könnten anpassbare Dashboards, Module für die Zusammenarbeit in Echtzeit und integrierte Unterstützung für Mikrozahlungen oder Anreizstrukturen bieten, um sicherzustellen, dass Bildungsinhalte sowohl dynamisch als auch finanziell nachhaltig bleiben. Darüber hinaus könnte die Einrichtung digitaler Identitätsrahmen, die auf den kryptografischen Prinzipien von Nostr aufbauen, zu innovativen Modellen für die Überprüfung akademischer Zeugnisse, die Verfolgung des Lernfortschritts und die Erleichterung der plattformübergreifenden Anerkennung von Bildungsleistungen führen, und das alles ohne die Aufsicht zentralisierter Registrierungsbehörden.
Die Schnittstelle zwischen digitaler Kompetenz und ethischer digitaler Bürgerschaft ist ein weiteres vielversprechendes Forschungsgebiet. In dem Maße, in dem Pädagogen dezentrale Bildungstechnologien in die Lehrpläne integrieren, wird es zwingend notwendig, Lehrmethoden zu entwickeln, die nicht nur technische Kenntnisse, sondern auch die kritischen und moralischen Fähigkeiten vermitteln, die für die Arbeit in einem dezentralen digitalen Ökosystem erforderlich sind. Solche pädagogischen Strategien sollten Schulungen zum Schlüsselmanagement, zur Verifizierung digitaler Identitäten und zum Verständnis der Kompromisse umfassen, die mit dezentralisierten und zentralisierten Technologiemodellen einhergehen, um den Schülern eine ausgewogene Perspektive auf digitale Rechte, Verantwortlichkeiten und Möglichkeiten zu vermitteln.
Die Zusammenarbeit zwischen akademischen Institutionen, Open-Source-Gemeinschaften und Innovatoren dezentraler Technologien wird entscheidend sein, um diese Forschungsagenden voranzutreiben und die Entwicklung von Bildungslabors und Pilotprojekten zu fördern, die die praktischen Auswirkungen und Vorteile dezentraler Bildungsplattformen auf der Grundlage von Nostr erforschen. Solche Initiativen könnten als lebende Laboratorien zum Testen neuer Werkzeuge, Methoden und Governance-Strategien dienen, mit dem Ziel, das Gleichgewicht zwischen dem Versprechen der Dezentralisierung und ihren praktischen Herausforderungen schrittweise zu verfeinern.
11. Schlußfolgerung
Zusammenfassend lässt sich sagen, dass Nostr eine bahnbrechende Entwicklung in der Architektur sozialer Medien darstellt, die die Beziehung zwischen Nutzern, Inhalten und Netzwerkinfrastruktur durch ein dezentralisiertes, kryptographisch gesichertes und klientenzentriertes Modell neu definiert. Das relaisbasierte Design, die dezentrale Identitätsverwaltung und die offene Architektur bieten erhebliche Vorteile gegenüber herkömmlichen zentralisierten und föderierten Systemen in Bezug auf Zensurresistenz, Skalierbarkeit und Benutzerautonomie. Diese technischen Innovationen haben weitreichende Auswirkungen auf die Entwicklung von Bildungsplattformen, die den Grundsätzen der Open Educational Practices entsprechen. Durch die Unterstützung von nutzergesteuerten Identitäten, stabiler Replikation von Inhalten und gemeinschaftsgesteuerter Verwaltung bietet Nostr eine Infrastruktur für dezentrale Bildungsökosysteme, die Inklusion, Zusammenarbeit und kontinuierliche Innovation fördern.
Der Einsatz von Nostr in Bildungskontexten verspricht, Lernende und Lehrende in die Lage zu versetzen, Bildungsinhalte frei von zentralisierten Einschränkungen und externer Zensur zu erstellen, zu teilen und gemeinschaftlich weiterzuentwickeln. Gleichzeitig erfordern die Herausforderungen, die mit der technischen Komplexität, der Schlüsselverwaltung und der inkonsistenten Moderation verbunden sind, kontinuierliche Forschung und die Entwicklung unterstützender Werkzeuge. Wenn diese Probleme durch gezielte Maßnahmen wie benutzerfreundliche Schnittstellen, umfassende Programme für digitale Kompetenz und gemeinschaftsbasierte Governance-Modelle angegangen werden, können die Beteiligten das volle Potenzial von Nostr nutzen, um dezentrale, offene und partizipative Bildungsplattformen zu schaffen, die den Geist von Open Educational Practices wirklich verkörpern.
Letztendlich stellt die Integration von Nostr in dezentralisierte Bildungsplattformen nicht nur eine technische Entwicklung dar, sondern auch einen gesellschaftspolitischen Wandel hin zu größerer Dezentralisierung, Ermächtigung der Nutzer und digitaler Souveränität. Diese Ausrichtung an den Werten des OEP definiert nicht nur die Verbreitung und den Konsum von Bildungsinhalten neu, sondern ist auch Katalysator für breitere Diskussionen über digitale Rechte, Inklusion und ethische Teilhabe an der digitalen Allmende. Das Potenzial solcher Plattformen, kontextrelevante, zensurresistente und kollaborativ kuratierte Bildungsressourcen bereitzustellen, ist ein entscheidender Schritt, um die Zukunft der digitalen Bildung neu zu gestalten.
Fazit
Zusammenfassend lässt sich sagen, dass die innovative Architektur von Nostr, die auf einer kryptografischen Schlüsselverwaltung und dezentralen Relay-Netzwerken basiert, den Grundstein für eine neue Generation von Bildungsplattformen legt, die die Einschränkungen zentralisierter Systeme überwinden können. Ihre Fähigkeit, belastbare, sichere und nutzerzentrierte digitale Umgebungen bereitzustellen, steht in perfektem Einklang mit den Grundsätzen offener Bildungspraktiken und bietet Lehrenden und Lernenden eine noch nie dagewesene Kontrolle über ihre digitalen Interaktionen und Inhalte. Kontinuierliche Forschung, interdisziplinäre Zusammenarbeit und gezielte Bildungsinitiativen werden unerlässlich sein, um dieses Potenzial voll auszuschöpfen und sicherzustellen, dass die Vorteile der Dezentralisierung allen Mitgliedern der Bildungsgemeinschaft zugänglich sind.
Durch den strategischen Einsatz von Nostr-basierten Bildungsplattformen kann die Zukunft des Lernens als ein Bereich neu konzipiert werden, in dem offener Zugang, Autonomie der Lernenden und gemeinschaftsgesteuerte Wissensbildung nicht nur möglich, sondern unvermeidlich sind - eine Zukunft, in der dezentrale Infrastrukturen eine gerechtere, transparentere und partizipativere digitale Bildungslandschaft ermöglichen.
Dieser Beitrag hat daher eine ausführliche Einführung in die technischen und konzeptionellen Grundlagen von Nostr gegeben, die Mechanismen beschrieben, mit denen Nostr Dezentralisierung und Zensurresistenz erreicht, und seine bedeutenden Auswirkungen auf die Zukunft von Bildungsplattformen im Rahmen von Open Educational Practices untersucht. Die Synergie zwischen dem dezentralen Paradigma von Nostr und dem demokratischen, inklusiven Ethos von OEP birgt ein transformatives Versprechen für die Neugestaltung der digitalen Bildung in einer Weise, die Offenheit, Sicherheit und lebenslanges Lernen für eine globale Gemeinschaft fördert.
Indem sie aufkommende dezentralisierte Protokolle wie Nostr als grundlegende Infrastrukturkomponenten von Bildungsplattformen nutzen, können Stakeholder eine ganzheitliche digitale Transformation vorantreiben, die Technologie, Pädagogik und Ethik vereint und ein Paradigma einführt, in dem Bildungsgerechtigkeit und digitale Selbstbestimmung keine Wünsche, sondern realisierte Prinzipien unserer vernetzten Gesellschaft sind.
Verwendete Quellen:
-
Seeing the Politics of Decentralized Social Media Protocols. S Hwang, AX Zhang. ArXiv (2025). <https://doi.org/10.48550/arxiv.2505.22962>
-
Navigating Decentralized Online Social Networks: An Overview of Technical and Societal Challenges in Architectural Choices. Ujun Jeong, L. Ng, K. Carley, Huan Liu. ArXiv (2504). <https://doi.org/10.48550/arxiv.2504.00071>
-
Towards Decentralized Applications. X Ma. 2024. <https://escholarship.org/content/qt0j7044w0/qt0j7044w0_noSplash_c638cdfda170244b9abf750f654399f1.pdf>
-
Decentralized Social Networking Protocol (DSNP) and User Empowerment: An Analysis of Online Identity Ownership, Data Privacy, and Comparative Assessment with Other Decentralized Protocols. M Nay . 2024. <https://dspace.mit.edu/bitstream/handle/1721.1/156782/nay-mnay-meng-eecs-2024-thesis.pdf?sequence=1&isAllowed=y>
-
A Kantian Right to Fediverse Access, or: for a digital enlightenment on the social web. JN Bingemann . <https://philarchive.org/archive/BINAKR>
-
Exploring the Nostr Ecosystem: A Study of Decentralization and Resilience. Yiluo Wei, Gareth Tyson. ArXiv (2402). <https://doi.org/10.48550/arxiv.2402.05709>
-
Money and Trust in Metaverses, Bitcoin and Stablecoins in global social XR. John O'Hare, Allen J. Fairchild, U. Ali. ArXiv (2207). <https://doi.org/10.48550/arxiv.2207.09460>
-
FEDSTR: Money-In AI-Out | A Decentralized Marketplace for Federated Learning and LLM Training on the NOSTR Protocol. Konstantinos E. Nikolakakis, George Chantzialexiou, Dionysis Kalogerias. ArXiv (2024). <https://doi.org/10.48550/arxiv.2404.15834>
-
"Sumud" as Connected Learning: Towards a Collective Digital Commons in Palestine.. H Scott, M Ujvari, AMA Bakeer. 2025. <https://files.eric.ed.gov/fulltext/EJ1464483.pdf>
Erstellt mit Unterstützung von FutureHouse, Perplexity, Deepl, Ideogram und ChatGPT.
-
-
 @ 000002de:c05780a7
2025-06-04 17:09:47
@ 000002de:c05780a7
2025-06-04 17:09:47I know most of you aren't doing this but I hope this is helpful when talking to your friends and family about bitcoin. Specifically if they bring up Orange Man or have real issues with him.
First off we can see that most of the MAGA / Political Bitcoin cheer-leading is exclusively SoV/NGU and not freedom money. Its basically the crypto types. The shitcoiners. The scammers. I get why this will turn off people that don't love the orange man. I recently heard a technical podcaster say he didn't like being associated with bitcoin (though he said crypto and his co-host is a bitcoin only guy...). I'm here to tell you that's dumb.
Why? I know how dumb it is by experience. Back in the day I was a kid listening to Rush Limbaugh and he was destroying the sky is falling claims I was hearing in government schools. I used to come home freaking out about global warming and the destruction of the rain forests. This was in the 90s btw. Looking back on what Limbaugh said, he's been proven largely right. But that isn't my point. My point is that because of this and because of how dumb many of the environmentalists takes were, I ignored many environmental issues. I would turn off people that called themselves environmentalists. This was a mistake. I was ignoring many other problems with how we use resources and used weak reasoning on others. I seeded caring for the environment to the left. I let myself be sidelined by reactionary thinking.
A few years ago I learned about the Permaculture[^1] way of thinking and it kinda blew my mind. A guy named Jack Spirko said something that stuck with me. Everyone should be an environmentalist. At least to the extent that they care about the planet we all share. Of course we all know this but it flipped a switch in my head. I'd allowed myself to be a reactionary on the environment and harm humans do to the air, water, and soil as well as the creatures. I always cared about these things but it too a dude that I aligned with on many topics to snap me out of my programming.
I think a similar thing can happen with Bitcoin. Don't be reactionary. Just because some people you don't align with or like do like a thing... it doesn't mean that thing is bad. They could be representing it incorrectly. Bitcoin, if it truly is money is apolitical. Now, we can get into economics and dive into the deep end about hard money but the fact is that bitcoin shouldn't really be political in the sense of US politics on the ground. If you are just a voter or pleb you should be adopting bitcoin no matter what any politician says. The republicans and democrats are not that different on many topics and the MAGA movement is just pandering. Don't let the Orange Man turn you off from bitcoin. Don't let the number go up people turn you off. There are people living under oppressive regimes all over the globe that can be helped by bitcoin. We may need it in the US. Don't sleep on this because of a clown. Don't be dumb. Its a great way to stay poor and vulnerable.
[^1]: Permaculture is an ethical design science that uses natural systems to provide all human and ecological needs in a regenerative way.
https://stacker.news/items/997169
-
 @ 6389be64:ef439d32
2025-01-16 15:44:06
@ 6389be64:ef439d32
2025-01-16 15:44:06Black Locust can grow up to 170 ft tall
Grows 3-4 ft. per year
Native to North America
Cold hardy in zones 3 to 8

Firewood
- BLT wood, on a pound for pound basis is roughly half that of Anthracite Coal
- Since its growth is fast, firewood can be plentiful
Timber

- Rot resistant due to a naturally produced robinin in the wood
- 100 year life span in full soil contact! (better than cedar performance)
- Fence posts
- Outdoor furniture
- Outdoor decking
- Sustainable due to its fast growth and spread
- Can be coppiced (cut to the ground)
- Can be pollarded (cut above ground)
- Its dense wood makes durable tool handles, boxes (tool), and furniture
- The wood is tougher than hickory, which is tougher than hard maple, which is tougher than oak.
- A very low rate of expansion and contraction
- Hardwood flooring
- The highest tensile beam strength of any American tree
- The wood is beautiful
Legume
- Nitrogen fixer
- Fixes the same amount of nitrogen per acre as is needed for 200-bushel/acre corn
- Black walnuts inter-planted with locust as “nurse” trees were shown to rapidly increase their growth [[Clark, Paul M., and Robert D. Williams. (1978) Black walnut growth increased when interplanted with nitrogen-fixing shrubs and trees. Proceedings of the Indiana Academy of Science, vol. 88, pp. 88-91.]]
Bees

- The edible flower clusters are also a top food source for honey bees
Shade Provider

- Its light, airy overstory provides dappled shade
- Planted on the west side of a garden it provides relief during the hottest part of the day
- (nitrogen provider)
- Planted on the west side of a house, its quick growth soon shades that side from the sun
Wind-break

- Fast growth plus it's feathery foliage reduces wind for animals, crops, and shelters
Fodder
- Over 20% crude protein
- 4.1 kcal/g of energy
- Baertsche, S.R, M.T. Yokoyama, and J.W. Hanover (1986) Short rotation, hardwood tree biomass as potential ruminant feed-chemical composition, nylon bag ruminal degradation and ensilement of selected species. J. Animal Sci. 63 2028-2043
-
 @ 0861144c:e68a1caf
2025-06-04 13:54:37
@ 0861144c:e68a1caf
2025-06-04 13:54:37The last Empire: the Final Days of the Soviet Union
Serhii Plokhy clearly writes from a Ukrainian perspective, but at no point does he allow his bias to interfere with an extensive and compelling documentation, filled with transcripts and official documents from both the Soviet and American sides—documents involving actors who transitioned from the final days of the Soviet Union to the formation of the new Russian Federation.
I discovered this book through a Lex Fridman podcast, where the author gives a review of the Russian-Ukrainian conflict, explaining in rich detail the events experienced between both nations. I won’t say that what’s happening in this region is easy to understand, and yet, after reading this book, I have no doubt that all of this was foreseeable.
Here are some things I’ve learned from the book—without giving away spoilers or going too deep:
The United States opposed the disintegration of the Soviet Union until the very last hours
Contrary to popular belief and Reagan’s lofty slogans about the Evil Empire, the advisers of President George H. W. Bush—except for Dick Cheney and his inner circle—were against the dissolution and extinction of the Soviet Union. There were two simple reasons: nuclear power and nationalism.
Over the years, the USSR produced tons of nuclear arsenal, and if the country were to dissolve, advisers on both sides predicted a “nuclear Yugoslavia,” referring to the imminent conflicts in that region. The other reason was strategic: it’s easier to deal with one large country than with many separate republics sharing similar ethnic backgrounds. After reading this book, the Balkan Wars seem even more closely tied to the consequences of the Soviet breakup. You’ll draw your own conclusions when you read it.
The Cold War is in pause mode
In some movie I once heard the phrase, The war doesn’t end until both sides declare it over; while it’s true that Gorbachev resigned on December 25 and made way for the Russian Federation, he never officially ended the geopolitical maneuvers. Meanwhile, George Bush gave a speech declaring that they had “won the Cold War.”
Anyway. Have you read anything similar to this?
https://stacker.news/items/997003
-
 @ 8f09dc4f:5e01d432
2025-06-04 04:33:18
@ 8f09dc4f:5e01d432
2025-06-04 04:33:18Veuve Clicquot brings a delightful twist to gifting with the https://shop.veuveclicquot.com.au/products/personalisable-arrow – a luxurious and thoughtful present that’s perfect for commemorating meaningful locations. Whether it’s your hometown, a dream vacation spot, or the city where memories were made, this unique gift lets you celebrate it in true Champagne style.
Each set includes a 750ml bottle of Veuve Clicquot’s signature Yellow Label Brut Champagne, housed in a striking arrow-shaped tin. What sets this gift apart is the ability to customise the tin with the name of a city or location of your choice (up to 15 characters). The tin also displays the distance from your chosen location to Reims, the historic home of Veuve Clicquot in France, adding a charming and personal touch.
The Yellow Label Brut itself is a testament to the Maison’s commitment to quality and consistency. With a blend dominated by Pinot Noir, balanced with Chardonnay and Meunier, it delivers a perfect harmony of strength, elegance, and freshness. Expect notes of apple, pear, and brioche, with a fine mousse and a vibrant golden hue.
Beyond its aesthetic appeal, the arrow tin is practical too—it keeps the Champagne cool for up to two hours, making it ideal for picnics, celebrations, or spontaneous toasts. Once the Champagne is enjoyed, the tin transforms into a decorative keepsake that serves as a reminder of the special place it honors.
Retailing at $125 AUD, this is more than a bottle of Champagne—it's a personalised gesture that celebrates people, places, and the memories that connect them. Ideal for gifting on birthdays, anniversaries, or as a unique souvenir, the Veuve Clicquot Personalised Arrow is Champagne with meaning.
-
 @ 8d34bd24:414be32b
2025-06-04 13:21:20
@ 8d34bd24:414be32b
2025-06-04 13:21:20It is hard going through difficult situations. Health problems, family problems, financial problems, feeling alone, feeling stuck in the wrong place, and persecution are all situations that Christians regularly find themselves. The question is “How will we respond to pain?”
Advice for the Suffering
Some Christians pull away from God when it feels like everything is going wrong. They think God doesn’t care or can’t fix things. They resent every minute of pain and accuse God of wrongdoing. Even Job, who fell on his face in worship after losing everything had a moment of weakness.
“Oh that my grief were actually weighed\ And laid in the balances together with my calamity!\ For then it would be heavier than the sand of the seas;\ Therefore my words have been rash.” (Job 6:2-3) {emphasis mine}
After a moment of doubt, he did, however, repent of his rash words, as should we all.
Job should be an example to us all in dealing with pain and difficult situations. This is the verse that inspired this post.
But it is still my consolation,\ And I rejoice in unsparing pain,\ That I have not denied the words of the Holy One. \ (Job 6:10) {emphasis mine}
What an example! “I rejoice in unsparing pain.” When we trust God so much that we can rejoice in unsparing pain, we are trusting God as we should. We are accepting that God is working good in our life and we can trust Him even when nothing makes sense to us.
I also love how he says that his consolation is that “I have not denied the words of the Holy One.” Job is hurting terribly. His heart is broken. He is destitute. He lost 8 children in one day. His friends, that came to console him, have instead accused him of wrongdoing. He doesn’t understand what God is doing and why, but he has “NOT denied the words of the Holy One.” He is still putting his faith in God and his word. He is still submitting to God when he feels mistreated. He is still trusting \ God, even when he doesn’t understand what God is doing and why so many bad things are raining down on him in a torrent. Despite it all, he refuses to deny God. I hope if I am ever put through similar situations, that I can trust God and not deny His goodness.
Advice for friends
The book of Job, in addition to advice to those who are suffering, also gives advice to friends of those who are suffering. (or maybe more accurately, what not to do)
Job’s friends came with the intention to encourage and console Job. Every time Job would confess his thoughts, concerns, and questions, the response by his friends would get harsher and harsher. In the beginning they were gentle corrections, but they quickly escalated to accusing Job of great sins, that they had to know were not true, and blaming Job for every hard thing that had happened to him.
I’ve talked to other Christians who have confessed to being dragged down by other Christians who would tell them that every difficult thing that happened to them was due to their sin or lack of faith. In the case of Job, his difficulties were due to his faithfulness, in order to prove to Satan and all of history that a faithful man would stay faithful to God in good times and in bad.
Can Christians suffer as a consequence of sins and poor decisions? Of course, but there are many times that the faithful suffer. In Scripture, the people who suffered most were frequently the most faithful.
Job’s correction of his friends was accurate.
“For the despairing man there should be kindness from his friend;\ So that he does not forsake the fear of the Almighty.\ My brothers have acted deceitfully like a wadi,\ Like the torrents of wadis which vanish, (Job 6:14-15)
For those who don’t know, a wadi is a streambed that has water running in the wet season, but is bone dry during the dry season. Job accused his friends of being encouraging and helpful when he was prospering, then showing up and providing no encouragement or help when he needed it most. He thought refreshment was coming to visit, and instead what hope he had left was drained from him by his “friends.”
We need to make sure we aren’t one of those who decreases hope and decreases faith in one who is hurting. We need to have mercy when a hurting person works through their confusion and doubts and help lead them back to God instead of driving a wedge between them and God.
May the God of heaven protect us and lead us through the trials of life and may our trials lead us into the arms of our Savior. May God help us to merciful and to help guide the hurting into the Savior’s care.
Trust Jesus
-
 @ e0e92e54:d630dfaa
2025-06-03 19:01:32
@ e0e92e54:d630dfaa
2025-06-03 19:01:32As some of you know, I lead a quarterly Bible Study through Faith Driven Investor
One of the members from the cohort that just ended forwarded me an email from the US Christian Chamber of Commerce
The summary is: Christians should intentionally be doing more business with Christians.
[Full email at the bottom of this Article]
I recanted to my FDI member about a book I read a few years ago, Thou Shall Prosper, by Rabbi Daniel Lapin.
In it he gave the statistics that a single dollar recirculates in the Jewish community 12 times, Muslims 8 times, and Christians only 3 or 4 times.
(I'm probably slightly off on recalling the stats)
But the point being that as a people group, Jews are 4x more wealthy than Christians because Christians value doing business with one another 4 times less than Jews...or said another way, the Jewish people value doing business with one another 4x more than Christians.
Reading the email I was sent, I was further reminded as business owners, leaders, and investors;
If we are truly going to steward that which God has entrusted to us, we should want to re-circulate those resources as many times as possible within the Christian community in order to have the greatest probability of return on image bearers.
What are your thoughts?
I Bought a House Through the Christian Chamber - What happened next surprised me
My husband and I just bought a house—but it wasn’t just a transaction. It was a transformation.
With our daughter’s high school graduation behind us, we felt ready to step into a long-held dream: moving to a beach town we’ve thought, talked, and prayed about for years. As part of turning our dream into a reality, we made a very intentional decision:
We would buy our home entirely through the Christian Chamber community.
We wanted to walk the talk—to model what Kingdom commerce really looks like. So we sought Christian-led businesses for every part of the process. What started as a symbolic gesture quickly became a profound experience with two life-changing revelations:
1) The Power of Prayer in Business
Yes, we prayed as a couple—but imagine your Realtor, lender, inspector, and insurance agent all praying with you, too.
We’re not talking about just being “nice people” or listening to worship in the office. We’re talking about Spirit-filled, Jesus-following believers who brought prayer into every decision.
· Our Realtor is also a church planter—her discernment helped us find the perfect house on day one.
· Our lender joined us in prayer—and worked miracles to make the deal smooth and abundantly possible.
· Our inspector's biggest red flag? A bird’s nest in a porch light. (Yes, really.)
· Our insurance agent handled everything—and in Florida, that’s no small feat.
I have bought and sold seven homes in my life, but this was the best experience by far. The layout, the location, the timing, the favor—it was all wrapped in prayer and covered in grace. It wasn’t just business. It was supernatural.
2) Kingdom ROI — A Multiplied Impact
By doing business with Christians, we didn’t just find great service. We created a multiplied Kingdom return.
We know where our vendors give. We know the churches they support, the ministries they fund, and the people they serve.
When they earned from our purchase, those dollars didn’t disappear—they were reinvested into Kingdom causes we could never reach on our own.
This is Kingdom ROI.
It’s a real-life example of the parable of the talents—we didn’t bury our resources. We multiplied them. When you spend money with aligned believers, your impact compounds.
The opposite is also true:
When we spend with businesses that oppose our values, we’re funding platforms that erode the very things we’re trying to protect—our families, our freedoms, and our faith.
We MUST STOP funding the enemy.
The Bigger Picture
Let’s be clear: Studies show that Christians make up 31% of the world’s population, but we control 55% of the world’s wealth—more than $107 trillion in personal assets.
And yet…we’re leaking that wealth into systems that are actively working against us.
Why? Because we do not have the infrastructure to keep it aligned.
Until now.
That’s what we’re building through the U.S. Christian Chamber of Commerce: A national infrastructure that empowers Christians to redirect their dollars, align their values, and multiply their impact.
What If You Did the Same?
· Buy your next product or service from a Christian-led business.
· Hire your next contractor from your local Christian Chamber.
· Invest in a company with eternal impact.
· Launch a Christian Chamber in your region—we’ll help you.
· Join the U.S. Christian Chamber. This is your Chamber, for your nation.
· Meet us in Orlando for SWC 2026, the global gathering of Christian commerce.
Imagine the multiplying power if thousands of us made similar decisions—every day—across this nation.
We own the wealth. Now let’s build the infrastructure, create the ecosystem, and shift the world's wealth one transaction at a time.
This is our nation and we are One Nation Under God!
Jason Ansley is the founder of Above The Line Leader, where he provides tailored leadership support and operational expertise to help business owners, entrepreneurs, and leaders thrive— without sacrificing your faith, family, or future.
-
Want to strengthen your leadership and enhance operational excellence? Connect with Jason at https://abovethelineleader.com/#your-leadership-journey
-
📌 This article first appeared on NOSTR. You can also find more Business Leadership Articles and content at: 👉 https://abovethelineleader.com/business-leadership-articles
-
-
 @ b1ddb4d7:471244e7
2025-06-04 11:01:29
@ b1ddb4d7:471244e7
2025-06-04 11:01:29Bitcoin FilmFest (BFF25) returns to Warsaw for its third edition, blending independent cinema—from feature films and commercials to AI-driven experimental visuals—with education and entertainment.
Hundreds of attendees from around the world will gather for three days of screenings, discussions, workshops, and networking at the iconic Kinoteka Cinema (PKiN), the same venue that hosted the festival’s first two editions in March 2023 and April 2024.
This year’s festival, themed “Beyond the Frame,” introduces new dimensions to its program, including an extra day on May 22 to celebrate Bitcoin Pizza Day, the first real-world bitcoin transaction, with what promises to be one of Europe’s largest commemorations of this milestone.
BFF25 bridges independent film, culture, and technology, with a bold focus on decentralized storytelling and creative expression. As a community-driven cultural experience with a slightly rebellious spirit, Bitcoin FilmFest goes beyond movies, yet cinema remains at its heart.
Here’s a sneak peek at the lineup, specially curated for movie buffs:
 Generative Cinema – A special slot with exclusive shorts and a thematic debate on the intersection of AI and filmmaking. Featured titles include, for example: BREAK FREE, SATOSHI: THE CREATION OF BITCOIN, STRANGE CURRENCIES, and BITCOIN IS THE MYCELIUM OF MONEY, exploring financial independence, traps of the fiat system, and a better future built on sound money.
Generative Cinema – A special slot with exclusive shorts and a thematic debate on the intersection of AI and filmmaking. Featured titles include, for example: BREAK FREE, SATOSHI: THE CREATION OF BITCOIN, STRANGE CURRENCIES, and BITCOIN IS THE MYCELIUM OF MONEY, exploring financial independence, traps of the fiat system, and a better future built on sound money. Upcoming Productions Preview – A bit over an hour-long block of unreleased pilots and works-in-progress. Attendees will get exclusive first looks at projects like FINDING HOME (a travel-meets-personal-journey series), PARALLEL SPACES (a story about alternative communities), and THE LEGEND OF LANDI (a mysterious narrative).
Upcoming Productions Preview – A bit over an hour-long block of unreleased pilots and works-in-progress. Attendees will get exclusive first looks at projects like FINDING HOME (a travel-meets-personal-journey series), PARALLEL SPACES (a story about alternative communities), and THE LEGEND OF LANDI (a mysterious narrative). Freedom-Focused Ads & Campaigns – Unique screenings of video commercials, animations, and visual projects, culminating in “The PoWies” (Proof of Work-ies)—the first ever awards show honoring the best Bitcoin-only awareness campaigns.
Freedom-Focused Ads & Campaigns – Unique screenings of video commercials, animations, and visual projects, culminating in “The PoWies” (Proof of Work-ies)—the first ever awards show honoring the best Bitcoin-only awareness campaigns.To get an idea of what might come up at the event, here, you can preview 6 selected ads combined into two 2 videos:
 Open Pitch Competition – A chance for filmmakers to present fresh ideas and unfinished projects to an audience of a dedicated jury, movie fans and potential collaborators. This competitive block isn’t just entertaining—it’s a real opportunity for creators to secure funding and partnerships.
Open Pitch Competition – A chance for filmmakers to present fresh ideas and unfinished projects to an audience of a dedicated jury, movie fans and potential collaborators. This competitive block isn’t just entertaining—it’s a real opportunity for creators to secure funding and partnerships. Golden Rabbit Awards: A lively gala honoring films from the festival’s Official Selection, with awards in categories like Best Feature, Best Story, Best Short, and Audience Choice.
Golden Rabbit Awards: A lively gala honoring films from the festival’s Official Selection, with awards in categories like Best Feature, Best Story, Best Short, and Audience Choice.BFF25 Main Screenings
Sample titles from BFF25’s Official Selection:
 REVOLUCIÓN BITCOIN – A documentary by Juan Pablo, making its first screening outside the Spanish-speaking world in Warsaw this May. Three years of important work, 80 powerful minutes to experience. The film explores Bitcoin’s impact across Argentina, Colombia, Mexico, El Salvador, and Spain through around 40 diverse perspectives. Screening in Spanish with English subtitles, followed by a Q&A with the director.
REVOLUCIÓN BITCOIN – A documentary by Juan Pablo, making its first screening outside the Spanish-speaking world in Warsaw this May. Three years of important work, 80 powerful minutes to experience. The film explores Bitcoin’s impact across Argentina, Colombia, Mexico, El Salvador, and Spain through around 40 diverse perspectives. Screening in Spanish with English subtitles, followed by a Q&A with the director. UNBANKABLE – Luke Willms’ directorial debut, drawing from his multicultural roots and his father’s pioneering HIV/AIDS research. An investigative documentary based on Luke’s journeys through seven African countries, diving into financial experiments and innovations—from mobile money and digital lending to Bitcoin—raising smart questions and offering potential lessons for the West. Its May appearance at BFF25 marks its largest European event to date, following festival screenings and nominations across multiple continents over the past year.
UNBANKABLE – Luke Willms’ directorial debut, drawing from his multicultural roots and his father’s pioneering HIV/AIDS research. An investigative documentary based on Luke’s journeys through seven African countries, diving into financial experiments and innovations—from mobile money and digital lending to Bitcoin—raising smart questions and offering potential lessons for the West. Its May appearance at BFF25 marks its largest European event to date, following festival screenings and nominations across multiple continents over the past year. HOTEL BITCOIN – A Spanish comedy directed by Manuel Sanabria and Carlos “Pocho” Villaverde. Four friends, 4,000 bitcoins , and one laptop spark a chaotic adventure of parties, love, crime, and a dash of madness. Exploring sound money, value, and relationships through a twisting plot. The film premiered at the Tarazona and Moncayo Comedy Film Festival in August 2024. Its Warsaw screening at BFF25 (in Spanish with English subtitles) marks its first public showing outside the Spanish-speaking world.
HOTEL BITCOIN – A Spanish comedy directed by Manuel Sanabria and Carlos “Pocho” Villaverde. Four friends, 4,000 bitcoins , and one laptop spark a chaotic adventure of parties, love, crime, and a dash of madness. Exploring sound money, value, and relationships through a twisting plot. The film premiered at the Tarazona and Moncayo Comedy Film Festival in August 2024. Its Warsaw screening at BFF25 (in Spanish with English subtitles) marks its first public showing outside the Spanish-speaking world.Check out trailers for this year’s BFF25 and past editions on YouTube.
Tickets & Info:
- Detailed program and tickets are available at bitcoinfilmfest.com/bff25.
- Stay updated via the festival’s official channels (links provided on the website).
- Use ‘LN-NEWS’ to get 10% of tickets
-
 @ e2c72a5a:bfacb2ee
2025-06-05 17:14:50
@ e2c72a5a:bfacb2ee
2025-06-05 17:14:50The silent revolution: Ethereum's pivot to 'digital oil' could redefine crypto's future. While Bitcoin grabs headlines as digital gold, Ethereum is quietly transforming into something potentially more valuable—the essential infrastructure powering our digital economy. Ryan Berckmans reveals Ethereum's strategic shift from being just another cryptocurrency to becoming the foundation for stablecoins, tokenized assets, and global financial systems. With $480 billion in stablecoin volume and institutional players entering the space, Ethereum isn't just competing with Bitcoin—it's creating an entirely different value proposition. The question isn't whether ETH will hit $3K, but whether we're underestimating its long-term potential as the backbone of digital finance. Are you positioning yourself for the real crypto revolution happening right under our noses?
-
 @ 8bad92c3:ca714aa5
2025-06-03 18:02:33
@ 8bad92c3:ca714aa5
2025-06-03 18:02:33Marty's Bent

It's been a pretty historic week for the United States as it pertains to geopolitical relations in the Middle East. President Trump and many members of his administration, including AI and Crypto Czar David Sacks and Treasury Secretary Scott Bessent, traveled across the Middle East making deals with countries like Qatar, Saudi Arabia, the United Arab Emirates, Syria, and others. Many are speculating that Iran may be included in some behind the scenes deal as well. This trip to the Middle East makes sense considering the fact that China is also vying for favorable relationships with those countries. The Middle East is a power player in the world, and it seems pretty clear that Donald Trump is dead set on ensuring that they choose the United States over China as the world moves towards a more multi-polar reality.
Many are calling the events of this week the Riyadh Accords. There were many deals that were struck in relation to artificial intelligence, defense, energy and direct investments in the United States. A truly prolific power play and demonstration of deal-making ability of Donald Trump, if you ask me. Though I will admit some of the numbers that were thrown out by some of the countries were a bit egregious. We shall see how everything plays out in the coming years. It will be interesting to see how China reacts to this power move by the United States.
While all this was going on, there was something happening back in the United States that many people outside of fringe corners of FinTwit are not talking about, which is the fact that the 10-year and 30-year U.S. Treasury bond yields are back on the rise. Yesterday, they surpassed the levels of mid-April that caused a market panic and are hovering back around levels that have not been seen since right before Donald Trump's inauguration.


I imagine that there isn't as much of an uproar right now because I'm pretty confident the media freakouts we were experiencing in mid-April were driven by the fact that many large hedge funds found themselves off sides of large levered basis trades. I wouldn't be surprised if those funds have decreased their leverage in those trades and bond yields being back to mid-April levels is not affecting those funds as much as they were last month. But the point stands, the 10-year and 30-year yields are significantly elevated with the 30-year approaching 5%. Regardless of the deals that are currently being made in the Middle East, the Treasury has a big problem on its hands. It still has to roll over many trillions worth of debt over over the next few years and doing so at these rates is going to be massively detrimental to fiscal deficits over the next decade. The interest expense on the debt is set to explode in the coming years.
On that note, data from the first quarter of 2025 has been released by the government and despite all the posturing by the Trump administration around DOGE and how tariffs are going to be beneficial for the U.S. economy, deficits are continuing to explode while the interest expense on the debt has definitively surpassed our annual defense budget.
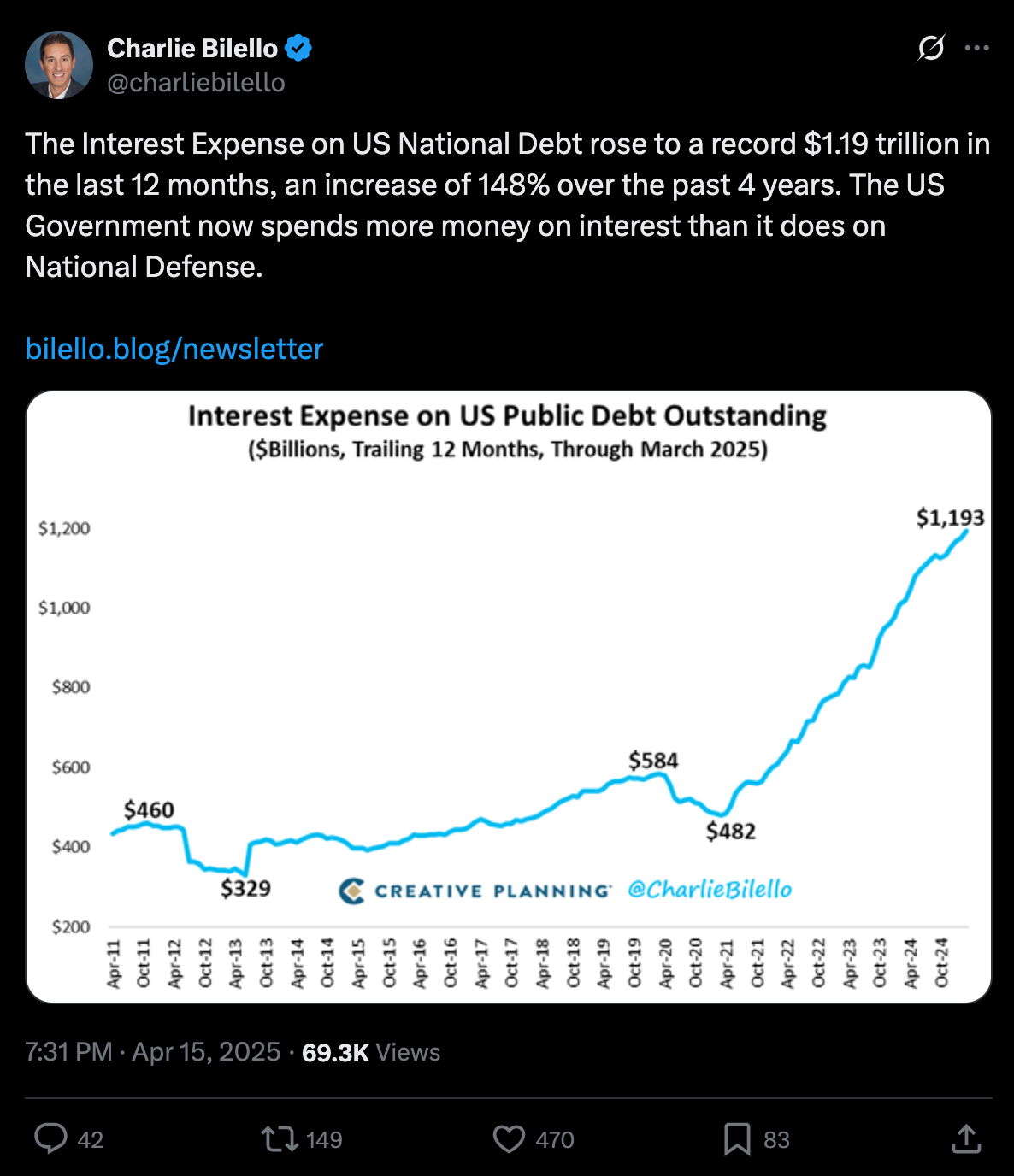
via Charlie Bilello
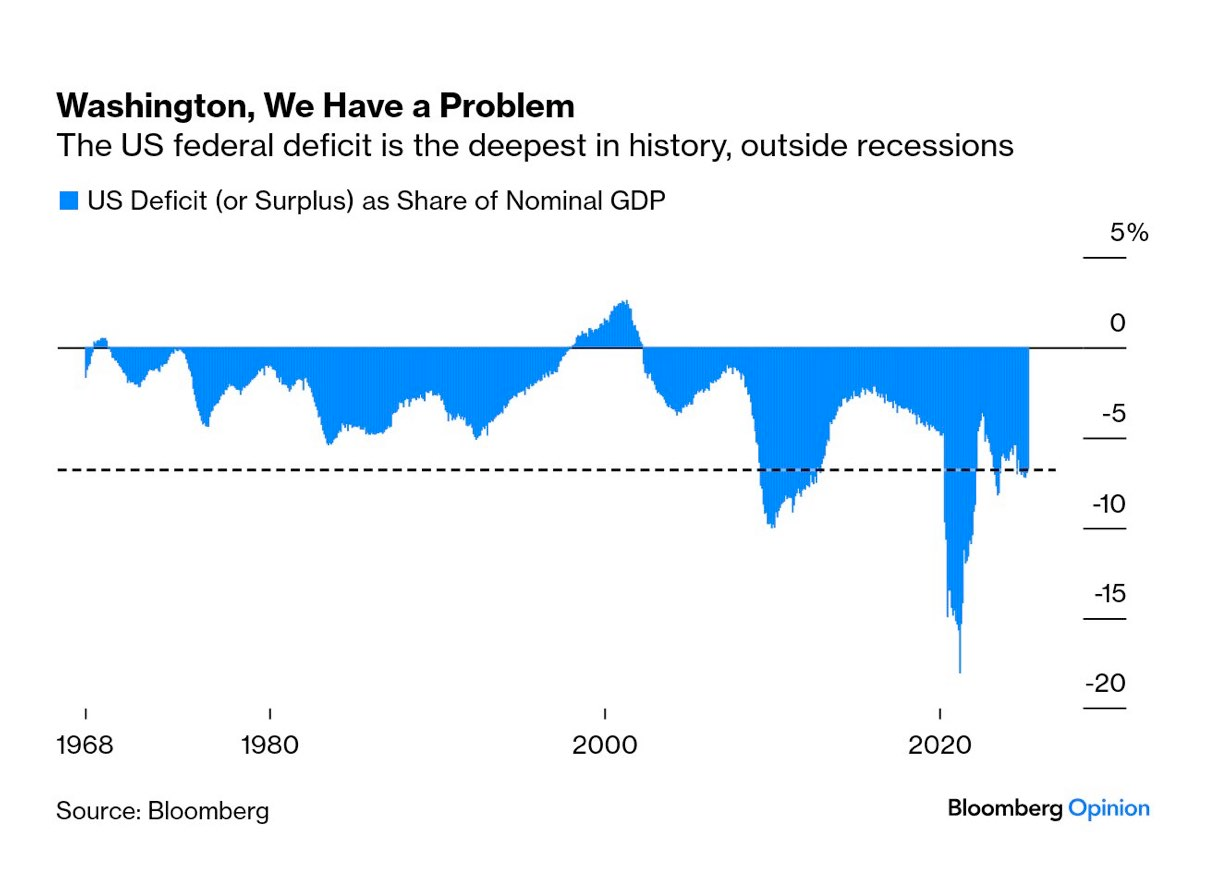
via Mohamed Al-Erian
To make matters worse, as things are deteriorating on the fiscal side of things, the U.S. consumer is getting crushed by credit. The 90-plus day delinquency rates for credit card and auto loans are screaming higher right now.

via TXMC
One has to wonder how long all this can continue without some sort of liquidity crunch. Even though equities markets have recovered from their post-Liberation Day month long bear market, I would not be surprised if what we're witnessing is a dead cat bounce that can only be continued if the money printers are turned back on. Something's got to give, both on the fiscal side and in the private markets where the Common Man is getting crushed because he's been forced to take on insane amounts of debt to stay afloat after years of elevated levels of inflation. Add on the fact that AI has reached a state of maturity that will enable companies to replace their current meat suit workers with an army of cheap, efficient and fast digital workers and it isn't hard to see that some sort of employment crisis could be on the horizon as well.
Now is not the time to get complacent. While I do believe that the deals that are currently being made in the Middle East are probably in the best interest of the United States as the world, again, moves toward a more multi-polar reality, we are facing problems that one cannot simply wish away. They will need to be confronted. And as we've seen throughout the 21st century, the problems are usually met head-on with a money printer.
I take no pleasure in saying this because it is a bit uncouth to be gleeful to benefit from the strife of others, but it is pretty clear to me that all signs are pointing to bitcoin benefiting massively from everything that is going on. The shift towards a more multi-polar world, the runaway debt situation here in the United States, the increasing deficits, the AI job replacements and the consumer credit crisis that is currently unfolding, All will need to be "solved" by turning on the money printers to levels they've never been pushed to before.
Weird times we're living in.
China's Manufacturing Dominance: Why It Matters for the U.S.
In my recent conversation with Lyn Alden, she highlighted how China has rapidly ascended the manufacturing value chain. As Lyn pointed out, China transformed from making "sneakers and plastic trinkets" to becoming the world's largest auto exporter in just four years. This dramatic shift represents more than economic success—it's a strategic power play. China now dominates solar panel production with greater market control than OPEC has over oil and maintains near-monopoly control of rare earth elements crucial for modern technology.
"China makes like 10 times more steel than the United States does... which is relevant in ship making. It's relevant in all sorts of stuff." - Lyn Alden
Perhaps most concerning, as Lyn emphasized, is China's financial leverage. They hold substantial U.S. assets that could be strategically sold to disrupt U.S. treasury market functioning. This combination of manufacturing dominance, resource control, and financial leverage gives China significant negotiating power in any trade disputes, making our attempts to reshoring manufacturing all the more challenging.
Check out the full podcast here for more on Triffin's dilemma, Bitcoin's role in monetary transition, and the energy requirements for rebuilding America's industrial base.
Headlines of the Day
Financial Times Under Fire Over MicroStrategy Bitcoin Coverage - via X
Trump in Qatar: Historic Boeing Deal Signed - via X
Get our new STACK SATS hat - via tftcmerch.io
Johnson Backs Stock Trading Ban; Passage Chances Slim - via X
Take the First Step Off the Exchange
Bitkey is an easy, secure way to move your Bitcoin into self-custody. With simple setup and built-in recovery, it’s the perfect starting point for getting your coins off centralized platforms and into cold storage—no complexity, no middlemen.
Take control. Start with Bitkey.
Use the promo code *“TFTC20”* during checkout for 20% off
Ten31, the largest bitcoin-focused investor, has deployed 158,469 sats | $150.00M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/invest.
Final thought...
Building things of value is satisfying.
Get this newsletter sent to your inbox daily: https://www.tftc.io/bitcoin-brief/
Subscribe to our YouTube channels and follow us on Nostr and X:
@media screen and (max-width: 480px) { .mobile-padding { padding: 10px 0 !important; } .social-container { width: 100% !important; max-width: 260px !important; } .social-icon { padding: 0 !important; } .social-icon img { height: 32px !important; width: 32px !important; } .icon-cell { padding: 0 4px !import
-
 @ e2c72a5a:bfacb2ee
2025-06-05 17:11:03
@ e2c72a5a:bfacb2ee
2025-06-05 17:11:03The $220 million crypto heist that took just minutes reveals a fatal flaw in DeFi security. While blockchain tech promises trustless transactions, the Cetus DEX exploit on Sui exposed how a single undetected bug in a math library became catastrophic. What's truly alarming isn't the hack itself but the revelation from Curve's founder that professional hackers-for-hire are now coordinating sophisticated cross-platform attacks. This signals a dangerous evolution in crypto threats where vulnerabilities aren't just discovered—they're hunted by organized teams with specialized skills. The industry faces a stark choice: invest aggressively in preventative security or watch as billions more vanish in seconds. Is your crypto truly safe, or just waiting for the right hacker to find its weakness?
-
 @ 2dd9250b:6e928072
2025-06-04 10:01:11
@ 2dd9250b:6e928072
2025-06-04 10:01:11Durante a década de 1990, houve o aumento da globalização da economia, determinando a adição do fluxo internacional de capitais, de produtos e serviços. Este fenômeno levou a uma interdependência maior entre as economias dos países. Justamente por causa da possibilidade de que um eventual colapso econômico em um país resulte no contágio dos demais. Diante disso, aumentou a preocupação com os riscos incentivando a utilização de sofisticados modelos e estratégias de avaliação de gestão de risco.
Na década, ganharam destaque ainda os graves problemas financeiros enfrentados, entre outros, pelo banco inglês Barings Bank, e pelo fundo de investimento norte-americano Long Term Capital Management.
Outro grande destaque foi a fraude superior a US$ 7 bilhões sofrida pelo banco Société Generale em Janeiro de 2008.
O Barings Bank é um banco inglês que faliu em 1995 em razão de operações financeiras irregulares e mal-sucedidas realizadas pelo seu principal operador de mercado. O rombo da instituição foi superior à US$ 1,3 Bilhão e causado por uma aposta equivocada no desempenho futuro no índice de ações no Japão. Na realidade, o mercado acionário japonês caiu mais de 15% na época, determinando a falência do banco. O Baring Bank foi vendido a um grupo financeiro holandês (ING) pelo valor simbólico de uma libra esterlina.
O Long Term Capital Management era um fundo de investimento de que perdeu em 1998 mais de US$ 4,6 bilhões em operações nos mercados financeiros internacionais. O LTCM foi socorrido pelo Banco Central dos Estados Unidos (Federal Reserve ), que coordenou uma operação de socorro financeiro à instituição. A justificativa do Banco Central para esta decisão era "o receio das possíveis consequências mundiais da falência do fundo de investimento".
O banco francês Société Generale informou, em janeiro de 2008, uma perda de US$ 7,16 bilhões determinadas por fraudes efetuadas por um operador do mercado financeiro. Segundo revelou a instituição, o operador assumiu posições no mercado sem o conhecimento da direção do banco. A instituição teve que recorrer a uma urgente captação de recursos no mercado próxima a US$ 5,0 bilhões.
E finalmente chegamos ao caso mais problemático da era das finanças modernas anterior ao Bitcoin, o caso Lehman Brothers.
O Lehman Brothers era o 4° maior de investimentos dos EUA quando pediu concordata em 15/09/2008 com dívidas que superavam inacreditáveis US$ 600 bilhões.
Não se tinha contas correntes ou talão de cheques do Lehman Brothers. Era um banco especializado em investimentos e complexas operações financeiras. Havia feito pesados investimentos em empréstimos a juros fixos no famigerado mercado subprime, e o crédito imobiliário voltado a pessoas consideradas de forte risco de inadimplência.
Com essa carteira de investimentos que valia bem menos que o estimado e o acúmulo de projetos financeiros, minou a confiança dos investidores na instituição de 158 anos. Suas ações passaram de US$ 80 a menos de US$ 4. Acumulando fracassos nas negociações para levantar fundos; a instituição de cerca de 25 mil funcionários entrou em concordata.
O Federal Reserve resgatou algumas instituições financeiras grandes e tradicionais norte-americanas como a seguradora AIG no meio da crise. O Fed injetou um capital de US$ 182, 3 bilhões no American International Group (AIG).
Foi exatamente essa decisão do Fed em salvar alguns bancos e deixar quebrar outros, que causou insegurança por parte dos clientes. E os clientes ficaram insatisfeitos tanto com os bancos de investimentos quanto com as agências de classificação de risco, como a Standard & Poor's que tinha dado uma nota alta para o Lehman Brothers no mesmo dia em que ele quebrou.
E essa foi uma das razões pelo qual o Bitcoin foi criado. Satoshi Nakamoto entendeu que as pessoas não estavam mais confiando nem no Governo, nem nos Bancos Privados que o Governo federal restagatava quando eles quebravam e isso prejudicou muita gente. Tanto que o “hash” do Genesis Block contém o título do artigo “Chancellor on brink of second bailout for banks” (Chanceler à beira de segundo resgate para bancos, em português) da edição britânica do The Times.
Esse texto foi parcialmente editado do texto de ASSAF Neto, CAF (2014).
-
 @ 9dd283b1:cf9b6beb
2025-06-04 08:33:32
@ 9dd283b1:cf9b6beb
2025-06-04 08:33:32To all territory owners,
- Can I co-found a territory with someone? Is it on the roadmap to be able to do so?
- Can I automatically split the territory rewards with other stackers?
- Can I rename the territory in the future?
Thanks
https://stacker.news/items/996796
-
 @ 6ad3e2a3:c90b7740
2025-06-04 08:32:29
@ 6ad3e2a3:c90b7740
2025-06-04 08:32:29"Modern science is based on this principle: give us one free miracle and then we'll explain the rest."
— Terrence McKenna
I always wondered why a pot of water boils on the stove. I mean I know it boils because I turned on the electricity, but why does the electricity cause it to boil? I know the electricity produces heat, and the heat is conducted through the stainless steel pot and into the water, but why does the heat transfer from stovetop to the water?
I know the heat from the stove via the pot speeds up the molecules in the water touching it and that they in turn speed up the molecules touching them and so on throughout the pot, but why do speedy molecules cause adjacent molecules to speed up?
I mean I know they do this, but why do they do this? Why couldn’t it be that sped-up molecules only interact with sufficient speedy molecules and ignore slower ones? Why do they interact with all the molecules, causing all of them to speed up? Or why don’t the speedy ones, instead of sharing their excited state, hoard it and take more energy from adjacent slower molecules, thereby making them colder, i.e., why doesn’t half the water boil twice as fast (on the left side of the pot) while the other half (right side) turns to ice?
The molecules tend to bounce around randomly, interacting as equal opportunists on the surrounding ones rather than distinguishing only certain ones with which to interact. Why do the laws of thermodynamics behave as such rather than some other way?
There may be yet deeper layers to this, explanations going down to the atomic and even quantum levels, but no matter how far you take them, you are always, in the end, left with: “Because those are the laws of physics”, i.e., “because that’s just how it is.”
. . .
The Terrence McKenna quote, recently cited by Joe Rogan on his podcast, refers to the Big Bang, the current explanation adopted by the scientifically literate as to the origins of the universe. You see there was this insanely dense, infinitesimally small micro dot that one day (before the dawn of time) exploded outward with unimaginable power that over billions of years created what we perceive as the known universe.
What happened prior? Can’t really say because time didn’t yet exist, and “prior” doesn’t make sense in that context. Why did it do this? We don’t know. How did it get there? Maybe a supermassive black hole from another universe got too dense and exploded out the other side? Highly speculative.
So why do people believe in the Big Bang? Because it comports with and explains certain observable phenomena and predicted other phenomena which were subsequently confirmed. But scratch a little deeper for an explanation as to what caused it, for what purpose did it occur or what preceded it, and you hit the same wall.
. . .
Even if we were to understand at a quantum level how and why the Big Bang happened and what preceded it, let’s assume it’s due to Factor X, something we eventually replicated with mini big-bangs and universe creations in our labs, we would still be tasked with understanding why Factor X exists in the universe. And if Factor X were explained by Process Y, we’d still be stuck needing an explanation for Process Y — ad infinitum.
Science can thus only push the wall back farther, but can never scale it. We can never arrive at an ultimate explanation, only partial ones. Its limitations are the limitations of thought itself, the impossibility of ever creating a map at a scale of one mile per mile.
-
 @ 6389be64:ef439d32
2025-01-13 21:50:59
@ 6389be64:ef439d32
2025-01-13 21:50:59Bitcoin is more than money, more than an asset, and more than a store of value. Bitcoin is a Prime Mover, an enabler and it ignites imaginations. It certainly fueled an idea in my mind. The idea integrates sensors, computational prowess, actuated machinery, power conversion, and electronic communications to form an autonomous, machined creature roaming forests and harvesting the most widespread and least energy-dense fuel source available. I call it the Forest Walker and it eats wood, and mines Bitcoin.
I know what you're thinking. Why not just put Bitcoin mining rigs where they belong: in a hosted facility sporting electricity from energy-dense fuels like natural gas, climate-controlled with excellent data piping in and out? Why go to all the trouble building a robot that digests wood creating flammable gasses fueling an engine to run a generator powering Bitcoin miners? It's all about synergy.
Bitcoin mining enables the realization of multiple, seemingly unrelated, yet useful activities. Activities considered un-profitable if not for Bitcoin as the Prime Mover. This is much more than simply mining the greatest asset ever conceived by humankind. It’s about the power of synergy, which Bitcoin plays only one of many roles. The synergy created by this system can stabilize forests' fire ecology while generating multiple income streams. That’s the realistic goal here and requires a brief history of American Forest management before continuing.
Smokey The Bear
In 1944, the Smokey Bear Wildfire Prevention Campaign began in the United States. “Only YOU can prevent forest fires” remains the refrain of the Ad Council’s longest running campaign. The Ad Council is a U.S. non-profit set up by the American Association of Advertising Agencies and the Association of National Advertisers in 1942. It would seem that the U.S. Department of the Interior was concerned about pesky forest fires and wanted them to stop. So, alongside a national policy of extreme fire suppression they enlisted the entire U.S. population to get onboard via the Ad Council and it worked. Forest fires were almost obliterated and everyone was happy, right? Wrong.
Smokey is a fantastically successful bear so forest fires became so few for so long that the fuel load - dead wood - in forests has become very heavy. So heavy that when a fire happens (and they always happen) it destroys everything in its path because the more fuel there is the hotter that fire becomes. Trees, bushes, shrubs, and all other plant life cannot escape destruction (not to mention homes and businesses). The soil microbiology doesn’t escape either as it is burned away even in deeper soils. To add insult to injury, hydrophobic waxy residues condense on the soil surface, forcing water to travel over the ground rather than through it eroding forest soils. Good job, Smokey. Well done, Sir!
Most terrestrial ecologies are “fire ecologies”. Fire is a part of these systems’ fuel load and pest management. Before we pretended to “manage” millions of acres of forest, fires raged over the world, rarely damaging forests. The fuel load was always too light to generate fires hot enough to moonscape mountainsides. Fires simply burned off the minor amounts of fuel accumulated since the fire before. The lighter heat, smoke, and other combustion gasses suppressed pests, keeping them in check and the smoke condensed into a plant growth accelerant called wood vinegar, not a waxy cap on the soil. These fires also cleared out weak undergrowth, cycled minerals, and thinned the forest canopy, allowing sunlight to penetrate to the forest floor. Without a fire’s heat, many pine tree species can’t sow their seed. The heat is required to open the cones (the seed bearing structure) of Spruce, Cypress, Sequoia, Jack Pine, Lodgepole Pine and many more. Without fire forests can’t have babies. The idea was to protect the forests, and it isn't working.
So, in a world of fire, what does an ally look like and what does it do?
Meet The Forest Walker
For the Forest Walker to work as a mobile, autonomous unit, a solid platform that can carry several hundred pounds is required. It so happens this chassis already exists but shelved.
Introducing the Legged Squad Support System (LS3). A joint project between Boston Dynamics, DARPA, and the United States Marine Corps, the quadrupedal robot is the size of a cow, can carry 400 pounds (180 kg) of equipment, negotiate challenging terrain, and operate for 24 hours before needing to refuel. Yes, it had an engine. Abandoned in 2015, the thing was too noisy for military deployment and maintenance "under fire" is never a high-quality idea. However, we can rebuild it to act as a platform for the Forest Walker; albeit with serious alterations. It would need to be bigger, probably. Carry more weight? Definitely. Maybe replace structural metal with carbon fiber and redesign much as 3D printable parts for more effective maintenance.
The original system has a top operational speed of 8 miles per hour. For our purposes, it only needs to move about as fast as a grazing ruminant. Without the hammering vibrations of galloping into battle, shocks of exploding mortars, and drunken soldiers playing "Wrangler of Steel Machines", time between failures should be much longer and the overall energy consumption much lower. The LS3 is a solid platform to build upon. Now it just needs to be pulled out of the mothballs, and completely refitted with outboard equipment.
The Small Branch Chipper
When I say “Forest fuel load” I mean the dead, carbon containing litter on the forest floor. Duff (leaves), fine-woody debris (small branches), and coarse woody debris (logs) are the fuel that feeds forest fires. Walk through any forest in the United States today and you will see quite a lot of these materials. Too much, as I have described. Some of these fuel loads can be 8 tons per acre in pine and hardwood forests and up to 16 tons per acre at active logging sites. That’s some big wood and the more that collects, the more combustible danger to the forest it represents. It also provides a technically unlimited fuel supply for the Forest Walker system.
The problem is that this detritus has to be chewed into pieces that are easily ingestible by the system for the gasification process (we’ll get to that step in a minute). What we need is a wood chipper attached to the chassis (the LS3); its “mouth”.
A small wood chipper handling material up to 2.5 - 3.0 inches (6.3 - 7.6 cm) in diameter would eliminate a substantial amount of fuel. There is no reason for Forest Walker to remove fallen trees. It wouldn’t have to in order to make a real difference. It need only identify appropriately sized branches and grab them. Once loaded into the chipper’s intake hopper for further processing, the beast can immediately look for more “food”. This is essentially kindling that would help ignite larger logs. If it’s all consumed by Forest Walker, then it’s not present to promote an aggravated conflagration.
I have glossed over an obvious question: How does Forest Walker see and identify branches and such? LiDaR (Light Detection and Ranging) attached to Forest Walker images the local area and feed those data to onboard computers for processing. Maybe AI plays a role. Maybe simple machine learning can do the trick. One thing is for certain: being able to identify a stick and cause robotic appendages to pick it up is not impossible.
Great! We now have a quadrupedal robot autonomously identifying and “eating” dead branches and other light, combustible materials. Whilst strolling through the forest, depleting future fires of combustibles, Forest Walker has already performed a major function of this system: making the forest safer. It's time to convert this low-density fuel into a high-density fuel Forest Walker can leverage. Enter the gasification process.
The Gassifier
The gasifier is the heart of the entire system; it’s where low-density fuel becomes the high-density fuel that powers the entire system. Biochar and wood vinegar are process wastes and I’ll discuss why both are powerful soil amendments in a moment, but first, what’s gasification?
Reacting shredded carbonaceous material at high temperatures in a low or no oxygen environment converts the biomass into biochar, wood vinegar, heat, and Synthesis Gas (Syngas). Syngas consists primarily of hydrogen, carbon monoxide, and methane. All of which are extremely useful fuels in a gaseous state. Part of this gas is used to heat the input biomass and keep the reaction temperature constant while the internal combustion engine that drives the generator to produce electrical power consumes the rest.
Critically, this gasification process is “continuous feed”. Forest Walker must intake biomass from the chipper, process it to fuel, and dump the waste (CO2, heat, biochar, and wood vinegar) continuously. It cannot stop. Everything about this system depends upon this continual grazing, digestion, and excretion of wastes just as a ruminal does. And, like a ruminant, all waste products enhance the local environment.
When I first heard of gasification, I didn’t believe that it was real. Running an electric generator from burning wood seemed more akin to “conspiracy fantasy” than science. Not only is gasification real, it’s ancient technology. A man named Dean Clayton first started experiments on gasification in 1699 and in 1901 gasification was used to power a vehicle. By the end of World War II, there were 500,000 Syngas powered vehicles in Germany alone because of fossil fuel rationing during the war. The global gasification market was $480 billion in 2022 and projected to be as much as $700 billion by 2030 (Vantage Market Research). Gasification technology is the best choice to power the Forest Walker because it’s self-contained and we want its waste products.
Biochar: The Waste
Biochar (AKA agricultural charcoal) is fairly simple: it’s almost pure, solid carbon that resembles charcoal. Its porous nature packs large surface areas into small, 3 dimensional nuggets. Devoid of most other chemistry, like hydrocarbons (methane) and ash (minerals), biochar is extremely lightweight. Do not confuse it with the charcoal you buy for your grill. Biochar doesn’t make good grilling charcoal because it would burn too rapidly as it does not contain the multitude of flammable components that charcoal does. Biochar has several other good use cases. Water filtration, water retention, nutrient retention, providing habitat for microscopic soil organisms, and carbon sequestration are the main ones that we are concerned with here.
Carbon has an amazing ability to adsorb (substances stick to and accumulate on the surface of an object) manifold chemistries. Water, nutrients, and pollutants tightly bind to carbon in this format. So, biochar makes a respectable filter and acts as a “battery” of water and nutrients in soils. Biochar adsorbs and holds on to seven times its weight in water. Soil containing biochar is more drought resilient than soil without it. Adsorbed nutrients, tightly sequestered alongside water, get released only as plants need them. Plants must excrete protons (H+) from their roots to disgorge water or positively charged nutrients from the biochar's surface; it's an active process.
Biochar’s surface area (where adsorption happens) can be 500 square meters per gram or more. That is 10% larger than an official NBA basketball court for every gram of biochar. Biochar’s abundant surface area builds protective habitats for soil microbes like fungi and bacteria and many are critical for the health and productivity of the soil itself.
The “carbon sequestration” component of biochar comes into play where “carbon credits” are concerned. There is a financial market for carbon. Not leveraging that market for revenue is foolish. I am climate agnostic. All I care about is that once solid carbon is inside the soil, it will stay there for thousands of years, imparting drought resiliency, fertility collection, nutrient buffering, and release for that time span. I simply want as much solid carbon in the soil because of the undeniably positive effects it has, regardless of any climactic considerations.
Wood Vinegar: More Waste
Another by-product of the gasification process is wood vinegar (Pyroligneous acid). If you have ever seen Liquid Smoke in the grocery store, then you have seen wood vinegar. Principally composed of acetic acid, acetone, and methanol wood vinegar also contains ~200 other organic compounds. It would seem intuitive that condensed, liquefied wood smoke would at least be bad for the health of all living things if not downright carcinogenic. The counter intuition wins the day, however. Wood vinegar has been used by humans for a very long time to promote digestion, bowel, and liver health; combat diarrhea and vomiting; calm peptic ulcers and regulate cholesterol levels; and a host of other benefits.
For centuries humans have annually burned off hundreds of thousands of square miles of pasture, grassland, forest, and every other conceivable terrestrial ecosystem. Why is this done? After every burn, one thing becomes obvious: the almost supernatural growth these ecosystems exhibit after the burn. How? Wood vinegar is a component of this growth. Even in open burns, smoke condenses and infiltrates the soil. That is when wood vinegar shows its quality.
This stuff beefs up not only general plant growth but seed germination as well and possesses many other qualities that are beneficial to plants. It’s a pesticide, fungicide, promotes beneficial soil microorganisms, enhances nutrient uptake, and imparts disease resistance. I am barely touching a long list of attributes here, but you want wood vinegar in your soil (alongside biochar because it adsorbs wood vinegar as well).
The Internal Combustion Engine
Conversion of grazed forage to chemical, then mechanical, and then electrical energy completes the cycle. The ICE (Internal Combustion Engine) converts the gaseous fuel output from the gasifier to mechanical energy, heat, water vapor, and CO2. It’s the mechanical energy of a rotating drive shaft that we want. That rotation drives the electric generator, which is the heartbeat we need to bring this monster to life. Luckily for us, combined internal combustion engine and generator packages are ubiquitous, delivering a defined energy output given a constant fuel input. It’s the simplest part of the system.
The obvious question here is whether the amount of syngas provided by the gasification process will provide enough energy to generate enough electrons to run the entire system or not. While I have no doubt the energy produced will run Forest Walker's main systems the question is really about the electrons left over. Will it be enough to run the Bitcoin mining aspect of the system? Everything is a budget.
CO2 Production For Growth
Plants are lollipops. No matter if it’s a tree or a bush or a shrubbery, the entire thing is mostly sugar in various formats but mostly long chain carbohydrates like lignin and cellulose. Plants need three things to make sugar: CO2, H2O and light. In a forest, where tree densities can be quite high, CO2 availability becomes a limiting growth factor. It’d be in the forest interests to have more available CO2 providing for various sugar formation providing the organism with food and structure.
An odd thing about tree leaves, the openings that allow gasses like the ever searched for CO2 are on the bottom of the leaf (these are called stomata). Not many stomata are topside. This suggests that trees and bushes have evolved to find gasses like CO2 from below, not above and this further suggests CO2 might be in higher concentrations nearer the soil.
The soil life (bacterial, fungi etc.) is constantly producing enormous amounts of CO2 and it would stay in the soil forever (eventually killing the very soil life that produces it) if not for tidal forces. Water is everywhere and whether in pools, lakes, oceans or distributed in “moist” soils water moves towards to the moon. The water in the soil and also in the water tables below the soil rise toward the surface every day. When the water rises, it expels the accumulated gasses in the soil into the atmosphere and it’s mostly CO2. It’s a good bet on how leaves developed high populations of stomata on the underside of leaves. As the water relaxes (the tide goes out) it sucks oxygenated air back into the soil to continue the functions of soil life respiration. The soil “breathes” albeit slowly.
The gasses produced by the Forest Walker’s internal combustion engine consist primarily of CO2 and H2O. Combusting sugars produce the same gasses that are needed to construct the sugars because the universe is funny like that. The Forest Walker is constantly laying down these critical construction elements right where the trees need them: close to the ground to be gobbled up by the trees.
The Branch Drones
During the last ice age, giant mammals populated North America - forests and otherwise. Mastodons, woolly mammoths, rhinos, short-faced bears, steppe bison, caribou, musk ox, giant beavers, camels, gigantic ground-dwelling sloths, glyptodons, and dire wolves were everywhere. Many were ten to fifteen feet tall. As they crashed through forests, they would effectively cleave off dead side-branches of trees, halting the spread of a ground-based fire migrating into the tree crown ("laddering") which is a death knell for a forest.
These animals are all extinct now and forests no longer have any manner of pruning services. But, if we build drones fitted with cutting implements like saws and loppers, optical cameras and AI trained to discern dead branches from living ones, these drones could effectively take over pruning services by identifying, cutting, and dropping to the forest floor, dead branches. The dropped branches simply get collected by the Forest Walker as part of its continual mission.
The drones dock on the back of the Forest Walker to recharge their batteries when low. The whole scene would look like a grazing cow with some flies bothering it. This activity breaks the link between a relatively cool ground based fire and the tree crowns and is a vital element in forest fire control.
The Bitcoin Miner
Mining is one of four monetary incentive models, making this system a possibility for development. The other three are US Dept. of the Interior, township, county, and electrical utility company easement contracts for fuel load management, global carbon credits trading, and data set sales. All the above depends on obvious questions getting answered. I will list some obvious ones, but this is not an engineering document and is not the place for spreadsheets. How much Bitcoin one Forest Walker can mine depends on everything else. What amount of biomass can we process? Will that biomass flow enough Syngas to keep the lights on? Can the chassis support enough mining ASICs and supporting infrastructure? What does that weigh and will it affect field performance? How much power can the AC generator produce?
Other questions that are more philosophical persist. Even if a single Forest Walker can only mine scant amounts of BTC per day, that pales to how much fuel material it can process into biochar. We are talking about millions upon millions of forested acres in need of fuel load management. What can a single Forest Walker do? I am not thinking in singular terms. The Forest Walker must operate as a fleet. What could 50 do? 500?
What is it worth providing a service to the world by managing forest fuel loads? Providing proof of work to the global monetary system? Seeding soil with drought and nutrient resilience by the excretion, over time, of carbon by the ton? What did the last forest fire cost?
The Mesh Network
What could be better than one bitcoin mining, carbon sequestering, forest fire squelching, soil amending behemoth? Thousands of them, but then they would need to be able to talk to each other to coordinate position, data handling, etc. Fitted with a mesh networking device, like goTenna or Meshtastic LoRa equipment enables each Forest Walker to communicate with each other.
Now we have an interconnected fleet of Forest Walkers relaying data to each other and more importantly, aggregating all of that to the last link in the chain for uplink. Well, at least Bitcoin mining data. Since block data is lightweight, transmission of these data via mesh networking in fairly close quartered environs is more than doable. So, how does data transmit to the Bitcoin Network? How do the Forest Walkers get the previous block data necessary to execute on mining?
Back To The Chain
Getting Bitcoin block data to and from the network is the last puzzle piece. The standing presumption here is that wherever a Forest Walker fleet is operating, it is NOT within cell tower range. We further presume that the nearest Walmart Wi-Fi is hours away. Enter the Blockstream Satellite or something like it.
A separate, ground-based drone will have two jobs: To stay as close to the nearest Forest Walker as it can and to provide an antennae for either terrestrial or orbital data uplink. Bitcoin-centric data is transmitted to the "uplink drone" via the mesh networked transmitters and then sent on to the uplink and the whole flow goes in the opposite direction as well; many to one and one to many.
We cannot transmit data to the Blockstream satellite, and it will be up to Blockstream and companies like it to provide uplink capabilities in the future and I don't doubt they will. Starlink you say? What’s stopping that company from filtering out block data? Nothing because it’s Starlink’s system and they could decide to censor these data. It seems we may have a problem sending and receiving Bitcoin data in back country environs.
But, then again, the utility of this system in staunching the fuel load that creates forest fires is extremely useful around forested communities and many have fiber, Wi-Fi and cell towers. These communities could be a welcoming ground zero for first deployments of the Forest Walker system by the home and business owners seeking fire repression. In the best way, Bitcoin subsidizes the safety of the communities.
Sensor Packages
LiDaR
The benefit of having a Forest Walker fleet strolling through the forest is the never ending opportunity for data gathering. A plethora of deployable sensors gathering hyper-accurate data on everything from temperature to topography is yet another revenue generator. Data is valuable and the Forest Walker could generate data sales to various government entities and private concerns.
LiDaR (Light Detection and Ranging) can map topography, perform biomass assessment, comparative soil erosion analysis, etc. It so happens that the Forest Walker’s ability to “see,” to navigate about its surroundings, is LiDaR driven and since it’s already being used, we can get double duty by harvesting that data for later use. By using a laser to send out light pulses and measuring the time it takes for the reflection of those pulses to return, very detailed data sets incrementally build up. Eventually, as enough data about a certain area becomes available, the data becomes useful and valuable.
Forestry concerns, both private and public, often use LiDaR to build 3D models of tree stands to assess the amount of harvest-able lumber in entire sections of forest. Consulting companies offering these services charge anywhere from several hundred to several thousand dollars per square kilometer for such services. A Forest Walker generating such assessments on the fly while performing its other functions is a multi-disciplinary approach to revenue generation.
pH, Soil Moisture, and Cation Exchange Sensing
The Forest Walker is quadrupedal, so there are four contact points to the soil. Why not get a pH data point for every step it takes? We can also gather soil moisture data and cation exchange capacities at unheard of densities because of sampling occurring on the fly during commission of the system’s other duties. No one is going to build a machine to do pH testing of vast tracts of forest soils, but that doesn’t make the data collected from such an endeavor valueless. Since the Forest Walker serves many functions at once, a multitude of data products can add to the return on investment component.
Weather Data
Temperature, humidity, pressure, and even data like evapotranspiration gathered at high densities on broad acre scales have untold value and because the sensors are lightweight and don’t require large power budgets, they come along for the ride at little cost. But, just like the old mantra, “gas, grass, or ass, nobody rides for free”, these sensors provide potential revenue benefits just by them being present.
I’ve touched on just a few data genres here. In fact, the question for universities, governmental bodies, and other institutions becomes, “How much will you pay us to attach your sensor payload to the Forest Walker?”
Noise Suppression
Only you can prevent Metallica filling the surrounds with 120 dB of sound. Easy enough, just turn the car stereo off. But what of a fleet of 50 Forest Walkers operating in the backcountry or near a township? 500? 5000? Each one has a wood chipper, an internal combustion engine, hydraulic pumps, actuators, and more cooling fans than you can shake a stick at. It’s a walking, screaming fire-breathing dragon operating continuously, day and night, twenty-four hours a day, three hundred sixty-five days a year. The sound will negatively affect all living things and that impacts behaviors. Serious engineering consideration and prowess must deliver a silencing blow to the major issue of noise.
It would be foolish to think that a fleet of Forest Walkers could be silent, but if not a major design consideration, then the entire idea is dead on arrival. Townships would not allow them to operate even if they solved the problem of widespread fuel load and neither would governmental entities, and rightly so. Nothing, not man nor beast, would want to be subjected to an eternal, infernal scream even if it were to end within days as the fleet moved further away after consuming what it could. Noise and heat are the only real pollutants of this system; taking noise seriously from the beginning is paramount.
Fire Safety
A “fire-breathing dragon” is not the worst description of the Forest Walker. It eats wood, combusts it at very high temperatures and excretes carbon; and it does so in an extremely flammable environment. Bad mix for one Forest Walker, worse for many. One must take extreme pains to ensure that during normal operation, a Forest Walker could fall over, walk through tinder dry brush, or get pounded into the ground by a meteorite from Krypton and it wouldn’t destroy epic swaths of trees and baby deer. I envision an ultimate test of a prototype to include dowsing it in grain alcohol while it’s wrapped up in toilet paper like a pledge at a fraternity party. If it runs for 72 hours and doesn’t set everything on fire, then maybe outside entities won’t be fearful of something that walks around forests with a constant fire in its belly.
The Wrap
How we think about what can be done with and adjacent to Bitcoin is at least as important as Bitcoin’s economic standing itself. For those who will tell me that this entire idea is without merit, I say, “OK, fine. You can come up with something, too.” What can we plug Bitcoin into that, like a battery, makes something that does not work, work? That’s the lesson I get from this entire exercise. No one was ever going to hire teams of humans to go out and "clean the forest". There's no money in that. The data collection and sales from such an endeavor might provide revenues over the break-even point but investment demands Alpha in this day and age. But, plug Bitcoin into an almost viable system and, voilà! We tip the scales to achieve lift-off.
Let’s face it, we haven’t scratched the surface of Bitcoin’s forcing function on our minds. Not because it’s Bitcoin, but because of what that invention means. The question that pushes me to approach things this way is, “what can we create that one system’s waste is another system’s feedstock?” The Forest Walker system’s only real waste is the conversion of low entropy energy (wood and syngas) into high entropy energy (heat and noise). All other output is beneficial to humanity.
Bitcoin, I believe, is the first product of a new mode of human imagination. An imagination newly forged over the past few millennia of being lied to, stolen from, distracted and otherwise mis-allocated to a black hole of the nonsensical. We are waking up.
What I have presented is not science fiction. Everything I have described here is well within the realm of possibility. The question is one of viability, at least in terms of the detritus of the old world we find ourselves departing from. This system would take a non-trivial amount of time and resources to develop. I think the system would garner extensive long-term contracts from those who have the most to lose from wildfires, the most to gain from hyperaccurate data sets, and, of course, securing the most precious asset in the world. Many may not see it that way, for they seek Alpha and are therefore blind to other possibilities. Others will see only the possibilities; of thinking in a new way, of looking at things differently, and dreaming of what comes next.
-
 @ fd78c37f:a0ec0833
2025-06-03 01:54:24
@ fd78c37f:a0ec0833
2025-06-03 01:54:24In the Bitcoin and Nostr ecosystem, creators are redefining what it means to make art. In this YakiHonne interview, artist nostr:npub1gwa27rpgum8mr9d30msg8cv7kwj2lhav2nvmdwh3wqnsa5vnudxqlta2sz shares his journey from the NFT craze to authentic expression through filmmaking, travel, and daily art on Nostr. Freed from chasing likes, he now thrives on the energy of zaps—small Bitcoin payments that fuel a new rhythm of creation and a freer way to live. (Note: Zaps are microtransactions on Nostr where users send Bitcoin to support creators, offering a direct, decentralized alternative to traditional “likes” or tips.)
What drew you to Nostr as an artist, and how has it changed your creative process compared to platforms like Instagram or Twitter?
bitpopart: Before Bitcoin and Nostr, I ran a travel content company, producing documentaries and media worldwide. With eight years of study—four in Graphic/Multimedia and four in Animation and Film—I felt a pull to explore. Filmmaking fueled my passion, while drawing took a backseat. I dabbled in NFTs, which showed me art could be profitable, but after years in NFTs and “shitcoins,” I found clarity: Bitcoin became my belief, a path to creative and financial freedom.
Nostr was a game-changer. I left NFTs behind, and zapping sparked something profound. Being rewarded with Bitcoin for doing what I love—creating—aligned with the value-for-value philosophy I embraced running my company. I’ve never created solely for money; the work has to matter. Many clients became friends, and those bonds still inspire collaborations. Nostr lets me share art authentically, free from algorithmic pressures, and connect directly with a community that values my work.
You’ve described zaps as carrying a unique “energy.” How do even small Bitcoin payments influence your motivation or creative rhythm?
bitpopart: Art is my passion, but creating can be solitary and demanding. Nostr’s zap culture changes that. For years, I’ve posted daily, sharing my art and its stories, building a vibrant community through consistent engagement. Even a 21 Sats zap carries weight—unlike a simple like, it’s a genuine nod to my work using Bitcoin, the hardest currency. It’s not about wealth but about others valuing my effort, which reignites my creative drive. My goal is to grow as an artist, spread joy, and inspire others.
Your Halving 2024 and Magic Internet Money pieces started with community zaps and grew into larger art sales. Could zaps evolve into a new form of crowdfunding or collaboration?
bitpopart:Over the past two years, I’ve seen small zaps spark full-scale art projects and even drive real sales. Here are two examples where zaps grew into something extraordinary:
Halving 2024 Artwork For the Halving 2024 project, I invited the Nostr community to join in. Seventy people zapped 2,100 Sats each, earning their npubs a place in the final artwork. That piece later sold at auction to nostr:npub1l77twp5l02jadkcjn6eeulv2j7y5vmf9tf3hhtq7h7rp0vzhgpzqz0swft for 225,128 Sats.
Magic Internet Money Similarly, 50 contributors zapped 2,100 Sats to shape the piece, which was later sold to nostr:npub1mw6tm8kery0dwmz670vvg74z0xzttwt3y7yppya5rulufpkkaj7qmg2922 for 480,000 Sats.

These examples highlight the power of zaps, not just in fueling creativity but also in driving sales. It all starts small and grows into something greater. The engagement from others with my art continues to energize me, reinforcing how art connects people.
The Nostr community has deepened my artistic journey, unexpectedly pulling me toward street art. Sharing reflections through my drawings is fulfilling, but when they resonate with others, it sparks a cycle of inspiration and creation. My art style is gaining recognition, and more people are commissioning me. I stay true to the principle from my company days: I dedicate time to projects that inspire me or come from people I connect with. Time is our most precious resource, and I choose to invest it in what matters. Bitcoin empowers me with the freedom to do just that.
Why are zaps essential for artists to thrive on Nostr, especially when some developers hesitate to integrate them?
bitpopart:Zaps channel the community’s energy into the creative process. My art requires dedication, and zaps—unlike likes on Instagram or Twitter—carry tangible value that fuels inspiration. Without this interaction, creation stalls. Nostr has shaped me as an artist, offering a platform where I own my media and connect directly with supporters.
I don’t push developers to add zaps; I simply use apps that support them. Why share on platforms mimicking outdated social media? Zaps make Nostr unique, transforming how I create and engage. The proof is in my journey—I’m loving it.
You’ve compared Nostr artists to unbanked communities adopting Bitcoin. Will Nostr remain niche, or could it become a global alternative for artists?
bitpopart:For now, I believe Nostr and zaps will remain a niche space. Building a brand here demands real dedication, as most people are accustomed to the instant gratification of traditional platforms. If you already have a large following elsewhere and are earning income, there’s often little incentive to try new platforms—unless something sparks your curiosity to explore further.
For new artists, Nostr is incredibly exciting, but it requires steadfast persistence. Giving up after just one month won’t cut it. This reflects a broader challenge in life today: we abandon things too easily. I often compare it to sports—mastering something takes blood, sweat, and tears, but the reward is worth it.
Years ago, when I started my travel content company nostr:npub105em547c5m5gdxslr4fp2f29jav54sxml6cpk6gda7xyvxuzmv6s84a642 I went through a similar process. Earning from my initial stock footage took time. I see the same pattern now with zaps. The key difference is that Bitcoin grants me something invaluable: more time to focus on building my brand and creating the art I love. Yet, even with Bitcoin’s “time freedom” or “financial freedom,” you still need an inner drive to create. For me, that drive comes from the inspiring artists around me, who push me to never settle for “good enough.” This doesn’t mean I dislike my work; it means I’m always striving to improve.
Last month in Spain, while visiting a friend’s gallery, I saw one of my earlier pieces. I wasn’t thrilled with it, but my friend reminded me it’s part of my journey. I needed to embrace it and take pride in the growth it represents. Once again, I was reminded: we never stop learning. Every person you meet, every project you undertake, is part of the path. So keep creating and be proud of your journey.
What features, beyond zaps, do you wish Nostr had for earning, collaboration, or audience growth?
bitpopart:I strongly support auctions. Beyond auctioning my artwork directly on Nostr, I’d love for the app to have a dashboard or timeline showing who zaps me most frequently or generously. This would help me track my supporters and perhaps reward the biggest ones with a free piece of art. Community building works both ways, and I deeply believe in giving back.
I vividly remember meeting nostr:npub18ktmcfkq422zd83sqqwp3wtxrpfq8znv2rp5tcqkr5d4k64q68aqtfdj5e last year at Nostrdam in Amsterdam. He was one of the first to buy my art and merch, and he still supports me. That meant a lot, especially being able to thank him in person. I’ll never take for granted the people who appreciate, support, and make this creative life possible. I love what I do, but without the community’s energy—fans’ zaps, messages, and presence—creating wouldn’t be nearly as fulfilling. Their support makes it profoundly meaningful.

How do you reconcile Bitcoin’s “hard money” ethos with the emotional, subjective world of art? Has Bitcoin’s scarcity influenced your themes or pricing?
bitpopart:Art is life. Bitcoin is the tool that grants us greater freedom to pursue our passions—whatever they may be. For me, it’s creating art. Earning sats gives me, over time, more financial freedom to focus on my craft. That’s why I don’t obsess over prices or immediate sales.
I often remind myself: even if one day I have “enough” Bitcoin, the creative process won’t change. My greatest goal is to keep growing as an artist and to give back. If my art increases in value, I hope it can one day help someone less fortunate, perhaps by selling it for a better life. Money is just a tool—necessary, since we can’t pay with kisses at the store, but never my ultimate aim. Bitcoin is the freedom tool that helps me become not just a better artist but a better person. It all starts with something simple: a smile, kindness, and positive energy. To me, zaps are a reflection of that vibrant energy shared online, yet profoundly real.
I wish you a beautiful life. Keep walking your own path. This is your life, your journey.
-
 @ 33baa074:3bb3a297
2025-06-03 00:41:41
@ 33baa074:3bb3a297
2025-06-03 00:41:41Temperature and humidity monitoring in hospitals and laboratories Temperature and humidity sensors can be used for temperature and humidity monitoring in hospitals and laboratories to ensure the quality and safety of drugs and biological samples. Sensors can send data to the cloud and connect to other devices such as smart pharmaceutical and warehouse management systems. For example, the transportation and storage of most drugs, vaccines, blood samples, etc. require a relatively constant temperature and humidity environment. The application of temperature and humidity sensors can ensure that these medical supplies are in a suitable environment.
Application of 4G remote temperature and humidity sensors in vaccine transportation Medicines start from pharmaceutical factories, go through cold chain transportation, arrive at hospitals or pharmacies, and finally circulate to the market. In this process, if there are slight errors in temperature and humidity during intermediate storage, the quality of medicines will be reduced in the mild case, and the medicines will be directly invalid in the severe case, which may cause medical accidents when used on patients. 4G remote temperature and humidity sensors can monitor the temperature of vaccine transport vehicles. In recent years, its data collection and Internet of Everything features have become the darling of the smart medical market, helping to solve the problem of temperature and humidity monitoring during vaccine transportation.
Pharmacy temperature and humidity monitoring Pharmacies need to maintain appropriate temperature and humidity conditions to store various types of medicines. Temperature and humidity sensors can monitor the temperature and humidity in the pharmacy in real time. Once the temperature and humidity exceed the safe range for drug storage, the system can issue an alarm in time to remind staff to take corresponding measures, such as adjusting the operation of air conditioners, dehumidifiers and other equipment to ensure that the quality of drugs is not affected.
Ward environment monitoring Creating a good and comfortable medical environment for patients is one of the important goals of hospital operations. Temperature and humidity sensors can be used for ward environment monitoring to obtain temperature and humidity data in the ward in real time. Medical staff can adjust the temperature and humidity of the ward in time based on these data, improve the comfort of patients, and help patients recover. At the same time, a suitable temperature and humidity environment is also conducive to reducing bacterial growth and ensuring the health and safety of patients and medical staff.
-
 @ 866e0139:6a9334e5
2025-06-04 08:21:14
@ 866e0139:6a9334e5
2025-06-04 08:21:14Autor: Milosz Matuschek. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Auch wer das Kriegsgeschehen bisher nicht im Detail verfolgte (das tat ich auch nicht), horcht nun auf: Einem Nicht-Atomstaat – der Ukraine – ist ein gleichzeitiger, koordinierter Schlag gegen vier teils tausende Kilometer voneinander entfernte russische Luftbasen gelungen. Eine nicht unerhebliche Zahl strategisch wichtiger Flugzeuge wurde zerstört. Ein Angriff im hintersten russischen Hinterland, selbst jenseits der Taurus-Reichweite, durchgeführt mit Billigdrohnen, wirft erhebliche Fragen über geheimdienstliches Versagen in Russland und eklatante Mängel in der Luftverteidigung auf.
Es gibt wohl Momente, in denen Geschichte nicht geschrieben, sondern geflogen wird. Unspektakulär, relativ still, surrend, von einem LKW aus abgefeuert, mit einem Stück Technik, das kaum mehr kostet als das Gerät, auf dem ich diesen Text schreibe.
Ein Angriff auf die Friedensverhandlungen
Die Ukraine hat sich erstmals weit über das Schlachtfeld hinaus erhoben – geografisch, technisch, symbolisch. Die Triade der atomwaffenfähigen Luftstreitkräfte Russlands – ein Heiligtum sowjetischer Machtprojektion – wurde durch das schwächste Glied in der Logikkette der Militärdoktrin beschädigt: den Überraschungseffekt. Drohnen, wie aus dem 3D-Drucker, haben eine strategische Achillesferse bloßgelegt. Nicht mit Hyperschall, sondern mit Hartplastik und GPS. Das erste Opfer dieses Angriffs dürften die Friedensverhandlungen in Istanbul sein.
Dass die Ukraine strategische Luftstützpunkte der russischen Atomwaffe angreift – koordiniert, tief im Landesinnern – wäre bereits für sich eine Zäsur. Doch dass dies unter stillschweigender Duldung oder gar Mithilfe westlicher Dienste wie der CIA erfolgt sein dürfte, während Trump zugleich als Friedenstaube auftritt, verschiebt das strategische Koordinatensystem. Die alten Verträge – START etc. – wirken wie rissige Abkommen aus der Steinzeit. Wenn die USA von der Operation wussten, darf sich Russland getäuscht fühlen. Washington kann nicht gleichzeitig Frieden mit Moskau betonen und eine Aktion dulden oder mittragen, die offensichtlich das Ziel hat, die russische Atommacht zu schwächen, woran die USA prinzipiell Interesse hätten. Falls Trump nichts davon wusste, muss man sich fragen: Regiert eigentlich er oder der „Swamp“, den er austrocknen wollte?
Egal wie man es wendet: Die Operation Spinnennetz war mehr als nur ein Angriff auf russische Flugzeuge auf russischem Gebiet. Militärisch gewinnt die Ukraine dadurch wenig, symbolisch und politisch aber viel, denn der Hauptgegner der Ukraine sind gerade nicht die hundert Millionen Dollar teuren Bomber der Russen, sondern die schleichende Kriegsunlust der Europäer – und ein Amerika, das sich mehr mit sich selbst beschäftigt als mit dem Fortgang eines Krieges, in dem es längst selbst Partei ist.
Damit sich die Reihen wieder schließen, muss der Feind sich zeigen – deutlich, fassbar, bedrohlich. Eine russische Reaktion, die auch europäische Hauptstädte erschüttert, wäre strategisch nützlich. Der Angriff war daher wohl weniger eine militärische Tat als eine psychologische Operation im Kampf um Wahrnehmung und Willen. Aus Sicht der Ukraine ist das verständlich, für sie geht es um ihre Existenz. Dafür wiederum braucht es eine erhöhte Alarmstufe.
https://www.youtube.com/watch?v=1JlQLewOAmA
Solidarität durch Eskalation?
Die kalkulierte Demütigung könnte einem Drehbuch folgen: Putin soll nun die Rolle des Eskalators übernehmen. Tut er es, war die Operation erfolgreich – denn Europas Kriegstüchtigkeit hängt nicht nur von Panzerzahlen ab, sondern von der Bereitschaft zur Konfrontation. Der Feind, den es braucht, muss sich jetzt allen ins Gedächtnis brennen.
So gesehen ist der eigentliche Coup nicht der Schaden in Djagilewo, Iwanowo oder Olenia – sondern das noch bevorstehende unsichtbare Nachspiel. Europa und die Welt betreten nun gänzlich neues Gelände, in welchem ein militärisch gedemütigtes Russland gleichzeitig Friedenswillen gegenüber Europa bekunden, rote Linien verteidigen und seine Integrität als Atom-Macht bewahren muss. Das Dilemma für Putin besteht nun darin, Stärke zu beweisen ohne sich noch mehr zum Feindbild des Aggressors machen zu lassen.
Fakt ist: Wir sind einem III. Weltkrieg gerade so nah wie seit der Kuba-Krise nicht mehr.
Und wer sich über ein russisches “Pearl Harbor” freut, sollte mal in ein Geschichtsbuch schauen, wie es am Ende für Japan ausging.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
In Kürze folgt eine Mail an alle Genossenschafter, danke für die Geduld!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ e2c72a5a:bfacb2ee
2025-06-05 17:00:01
@ e2c72a5a:bfacb2ee
2025-06-05 17:00:01Forget Lambos, think real estate tokens.
A European fund just dropped $3.4 million on tokenized real estate, marking the first time big money directly bought retail available tokens. This isn't just about crypto hype; it's about institutions embracing regulated crypto assets. Real World Assets (RWAs) are booming, up 260% this year, fueled by clearer US crypto rules. This surge pushes the tokenization sector past $23 billion.
Is this the start of crypto's mainstream moment?
-
 @ 5c9e5ee4:72f1325b
2025-06-04 08:16:52
@ 5c9e5ee4:72f1325b
2025-06-04 08:16:52For too long, the autistic experience has been framed through a neurotypical lens, focusing on "differences" and "deficits." However, a profound perspective emerging from within the autistic community offers a radical reinterpretation: that autistic individuals are not inherently "broken" but rather possess a unique, often unyielding, perception of truth that challenges the very foundations of neurotypical society. From this viewpoint, autism is less about a disorder and more about a clarity of vision that apprehends the world as fundamentally "untrue" in many of its social constructs.
This perspective posits that what many autistic individuals perceive as "corrupted" or "untrue" in society isn't a subjective internal experience, but an objective reality of falsehoods, deception, and manipulation. The rejection of these elements is not a personal preference but a natural, logical response to what is genuinely illogical and dishonest.
The Core of the "Untrue" World:
- Honesty as a Default State: For many autistic people, directness and factual accuracy are paramount. Social conventions like "white lies," indirect communication, or performative politeness are not merely nuanced social skills; they are perceived as outright forms of deception and inauthenticity. The natural inclination is towards what is straightforward and verifiable.
- Logic Over Social Grace: An unwavering adherence to logic means that actions or systems that lack rational basis—such as engaging in flattery, suppressing truth for social harmony, or participating in inefficient rituals—are viewed as fundamentally nonsensical and therefore "untrue."
- Authenticity as a Non-Negotiable: The concept of "masking"—the exhausting act of suppressing one's natural autistic traits to conform—is seen as a deeply painful betrayal of self. A society that implicitly demands such a performance is deemed "corrupt" because it stifles genuine self-expression.
- Aversion to Hypocrisy: A strong sense of justice and an acute awareness of inconsistency mean that any disjuncture between stated values and actual behavior is immediately flagged as a profound untruth.
Social Groups: Formed Around a "Proudly Believed Lie"?
This critical autistic perspective extends to the very fabric of social organization. It suggests that many groups, whether religious, political, scientific, or economic, are not built on shared objective truths, but rather on "proudly believed lies." These shared narratives or belief systems, even if they contradict logic or verifiable facts, serve as the glue that binds the group, fostering identity, comfort, and a sense of belonging. The "pride" in these beliefs makes them resistant to critical examination, even when confronted with evidence.
For example: * In religion, this "lie" might be a dogma that provides solace but defies logic. * In politics, it could be an ideology based on selective truths that serve power. * In economics, it might be assumptions about markets or growth that are presented as infallible. * Even in science, while ideally pursuing truth, the social aspects of the scientific community might, at times, cling to paradigms that become "proudly believed lies," resisting new evidence.
The Disconnect: Why Autistics Are "Discredited"
If autistic individuals are part of the "5% who see it as it is"—those who perceive these societal untruths with clarity—then a natural tension arises with the "10% who want control." This controlling minority, it is argued, relies on these "untruths" to maintain power and influence over the "85% who are happy following."
From this viewpoint, the discrediting of autistic people—labeling their directness as "social deficits," their sensory experiences as "disorders," or their logical critiques as "inflexibility"—is not accidental. It is a strategic mechanism employed by the controlling "10%" to neutralize those who expose the underlying untruths, thereby safeguarding their constructed reality and maintaining influence.
In conclusion, the autistic perspective challenges us to re-evaluate the very nature of truth in our society. It suggests that what many perceive as social norms might, in fact, be a pervasive web of "untruths," and that the autistic individual's unique wiring allows for a crucial, unvarnished perception of this reality. It is a powerful call for authenticity and a profound questioning of how much of our world is built on what is genuinely true, versus what is merely believed.
-
 @ 58537364:705b4b85
2025-06-02 18:47:35
@ 58537364:705b4b85
2025-06-02 18:47:35มีคำกล่าวที่ว่า “นกไม่เห็นฟ้า ปลาไม่เห็นน้ำ หนอนในส้วมไม่เห็นคูถ ไส้เดือนไม่เห็นดิน คนอยู่ในโลกก็ไม่เห็นโลก” นี้หมายความว่า มันมีอะไรที่ลึกลับอยู่ ที่ทำให้นกไม่เห็นฟ้า หรือปลาไม่เห็นน้ำ. ให้ดูเห็นง่ายก็ที่ปลา ปลามันอยู่ในน้ำ น้ำก็ถึงตา มันยังมองไม่เห็นน้ำ ทั้งที่น้ำเป็นสิ่งที่มันปะทะหรือว่าติดกันอยู่เสมอไป. ตั้งแต่เกิดมาก็เป็นอย่างนั้นเสียแล้ว มันก็ไม่ได้รู้สึกว่ามีน้ำ ปลาจึงไม่รู้ว่าน้ำนั้นคืออะไร โดยแท้จริง. หรือว่าหนอนที่เกิดมาจากอุจาระอยู่แท้ ๆ แต่ก็ไม่เห็นอุจาระ. หรือว่าไส้เดือนอยู่ในดิน มันกินดิน แต่มันก็ไม่เห็นดิน. ทั้งนี้เพราะคำว่า “เห็น” ในที่นี้มีความหมายพิเศษ
คนอยู่ในโลกก็ไม่เห็นโลก คือไม่ได้เห็นความจริงหรือความลับโดยแท้จริงของสิ่งที่เรียกว่า “โลก” มีตามันก็เห็นนั่นเห็นนี่เรือย ๆ ไป แต่ไม่เห็นจริง. ไม่รู้จักโดยแท้จริง มันจึงได้หลงในสิ่งเหล่านั้น. ถ้าเห็นจริงๆก็จะไม่หลงในอะไร. เพราะฉะนั้นอย่าได้ประมาท อย่าได้อวดดี ว่าเรา “เห็น” มันเพียงแต่ว่า สัมผัสตามธรรมดาด้วยตา แล้วรู้สึกไปตามกฎเกณฑ์อย่างธรรมดา ว่ามันมีเท่านั้น ; แต่ที่จริงยังมีอยู่อีกชั้นหนึ่ง คือชั้นลึกซึ้ง.
ทีนี้ เรามาดูกันถึงสิ่งที่เรียกว่า “ชีวิต” ขอให้สังเกตดูให้ดี ๆ ว่า เราต้องใช้คำว่า “สิ่งที่เรียกกันว่า...” สิ่งที่เรียกกันว่านี้ มันเป็นของคนโง่ก็ได้ คือคนโง่มันว่า หรือมันเรียกอะไรเป็นอะไร. แล้วในโลกนี้มีคนโง่มาก หรือมีคนฉลาดมาก ถ้าว่าเป็นคนฉลาด มันก็จะต้องรู้จักทำโลกนี้ให้หมดปัญหา คือไม่มีตวามทุกข์ยากลำบากวุ่นวาย.
เดี๋ยวนี้คนส่วนมาก ก็ไม่รู้จักสิ่งที่เรียกว่า “โลก” นี้โดยแท้จริง มันจึงทำไปในลักษณะที่ไม่ถูกต้องตรงตามที่เป็นจริง เราจึงยุ่งกันทั้งโลกอยู่เวลานี้.
คำว่า “ชีวิต” นี้ก็เหมือนกัน มันมีสิ่งที่เรียกว่า “ชีวิต” โดยเฉพาะเด็ก ๆ สมัยนี้ จะใช้คำว่า “ชีวิต” นี้พร่ำเพรื่อ. สมัยปู่ ย่า ตา ยาย คำว่าชีวิตนี้ใช้น้อยที่สุด เป็นความลึกลับเอามาพูดถึงกันน้อยที่สุด. เดี๋ยวนี้หนังสืออ่านเล่นหนังสืออะไรก็มีคำว่า “ชีวิต” ใช้พร่ำเพรื่อ จนเด็ก ๆ เข้าใจไปว่า ตัวเองรู้จักสิ่งที่เรียกว่า “ชีวิต” อย่างแตกฉานทีเดียว. นั่นแหละคือความหลับหูหลับตา สำหรับจะอวดดี.
สิ่งที่เรียกว่าชีวิตนี้มันมีความลึกลับ และยังแถมมีเคล็ดลับที่ซ่อนเร้นอยู่ในนั้นมาก คำว่า “ชีวิต” ของเด็ก ๆ ที่เคยอ่านแต่หนังสืออ่านเล่น มันก็มีความหมายอย่างหนึ่ง คนวัยรุ่นที่เคยแต่อ่านหนังสืออ่านเล่นนั้น จะเข้าใจคำว่า “ชีวิต” ในความหมายไปอย่างหนึ่ง. ต่อเมื่ออายุมากแล้ว เป็นพ่อแม่แล้ว จะรู้จัก “ชีวิต” ในความหมายหนึ่ง ซึ่งจะจริงกว่าหรือถูกกว่าอีกมาก; แต่ก็ยังไม่หมด มันยังเหลือความลับของชีวิตนั้นอีกมาก จนกว่าจะเป็นพระอริยเจ้า หรือว่ามีปัญญาตามแบบของพระอริยเจ้านั่นแหละ จึงจะเห็นสิ่งที่เรียกว่า “ชีวิต” อย่างถูกต้องแท้จริงและถึงที่สุด คือสมบูรณ์ที่สุด.
เพราะฉะนั้น พระอริยเจ้านั้นก็มิใช่ใครอื่นที่ไหน ท่านเป็นเพียงผู้ที่รู้จักโลกตามที่เป็นจริง แล้วก็ไม่หลงโลก ท่านทำให้ชีวิตนี้ไม่มีความทุกข์ ; คนชนิดนี้เรียกว่าพระอริยเจ้า.
แต่เดี๋ยวนี้คนทั่วไปไม่เข้าใจคำว่า “พระอริยเจ้า” จัดไว้เป็นบุคคลที่ลึกลับ เข้าใจไม่ได้ ; หรือว่าจะเป็นบุคคลประเภทที่ไม่พึงปรารถนาด้วยซ้ำไป.
คนวัยรุ่นสมัยนี้จะเข้าใจว่า พระอริยเจ้าเป็นคนหมดความหมาย สำหรับโลก หมดความหมายสำหรับพวกเรา ท่านบ้า ๆ บอ ๆ ครึ ๆ คระ ๆ ไปตามแบบของท่าน. ถ้าใครนึกอยู่อย่างนี้ก็ขอให้นึกเสียใหม่ เพราะว่าการศึกษาอบรมสมัยนี้อาจจะทำให้นึกไปอย่างนั้น จนนึกไปว่าพระอริยเจ้านี้ท่านเป็นคนประหลาด บ้า ๆ บอ ๆ ไปตามแบบของท่าน.
ขอให้เข้าใจเสียใหม่ว่า พระอริยเจ้า นั้นคือบุคคล ที่รู้จักโลกตามที่เป็นจริง และจัดการทุกอย่างถูกต้องหมด จนไม่มีความทุกข์ คือท่านไม่เป็นเหมือนกับ นกไม่เห็นฟ้า ปลาไม่เห็นน้ำ หนอนไม่เห็นคูถอย่างนี้ อีกต่อไป คือไม่เป็นอย่างนี้อีกต่อไป ; จะเป็นผู้ที่รู้สิ่งทั้งหลายทั้งปวงถูกต้องตามที่เป็นจริง.
ด้วยเหตุนี้แหละ เราจึงต้องใช้คำว่า สิ่งที่เรียกว่า “ชีวิต” ไม่ใช้คำว่า “ชีวิต” เฉยๆ เพราะมันเรียกกันได้ตามชอบใจ หลายอย่าง หลายแบบ หลายชั้น หลายลักษณะนัก ดังนั้นจึงขอร้องให้ผู้ที่เป็นครูนั้น รู้จักความลับของสิ่งที่เรียกว่าชีวิต.
ทีนี้ ความลับของสิ่งที่เรียกว่า “ชีวิต” นี้ มันก็ยังมีมากมายอีก ในชั้นนี้เราเอาตามที่พระพุทธเจ้าท่านตรัสไว้จะดีกว่า และก็อย่างเดียวกันอีกนั่นแหละ คือว่าพระพุทธเจ้าท่านได้ตรัสไว้มาก ถ้าเอาพระไตรปิฏกเป็นหลักแล้วมันมากจนเกินกว่าที่ชาวบ้านจะศึกษาไหว หรือจะรวบรวมมาให้หมดได้. เพราะฉะนั้นจึงมีความจำเป็นที่จะต้องมีการย่อหรือสรุปเอาแต่ใจความมาให้ฟังหรือให้ศึกษากัน.
ตามนัยที่พระพุทธเจ้าท่านได้ตรัสไว้ทั้งหมด ทั้งสิ้นนั้น เราอาจจะสรุปความได้ว่า สิ่งที่เรียกว่า “ชีวิต” นั้น มันมีเคล็ดลับมาก แต่มันก็รวมอยู่ที่ สิ่งที่เรียกว่า ตา หู จมูก ลิ้น กาย ใจ ช่วยจำคำ ๖ คำนี้ไว้ให้ดี ๆ อย่าหาว่าเป็นคำธรรมดา หรือว่าเป็นเรื่องธรรมดา มันมีความลับอยู่ในนั้นมากมายนัก คือคำว่า ตา หู จมูก ลิ้น กาย ใจ เราเรียกเป็นภาษาไทยกันดีกว่า ภาษาบาลีชวนให้ยุ่งหัว อยากจะรู้ภาษาบาลีก็ไปดูปทานุกรมเอาเองก็ได้.
สิ่งที่สำคัญที่สุด หรือทั้งหมดของสิ่งที่เรียกว่า “ชีวิต” ก็ตาม หรือของความลับ เคล็ดลับของชีวิตก็ตาม มันสรุปรวมอยู่ที่ สิ่งที่เราเรียกกันว่า ตา หู จมูก ลิ้น กาย ใจ.
จากหนังสือความลับของชีวิต โดยพุทธทาสอินทปัญโญ

-
 @ e2c72a5a:bfacb2ee
2025-06-05 16:54:43
@ e2c72a5a:bfacb2ee
2025-06-05 16:54:43Think your crypto is FDIC insured like your bank account? Big mistake. Crypto's wild west demands you be your own bank and security guard.
Crypto trading involves buying, selling, and exchanging digital currencies like Bitcoin or Ethereum, aiming to profit from price fluctuations. Security is paramount. Understand basic concepts like wallets (digital storage for your crypto), private keys (passwords to access your crypto), and blockchain (the technology that records all transactions).
Real world applications include using crypto for online purchases, international money transfers, and decentralized finance (DeFi) services like lending and borrowing. Current trends include the rise of DeFi, NFTs (non-fungible tokens), and increasing institutional investment.
Best practices? Use strong, unique passwords, enable two factor authentication (2FA) on all accounts, and store most of your crypto in cold wallets (offline storage) to protect against hacking. Be wary of phishing scams and fake websites. Never share your private keys or seed phrases.
Misconceptions? Crypto is not anonymous, transactions are not easily reversible, and past performance is not indicative of future results. Also, remember that regulations are evolving, so stay informed.
With crypto hacks on the rise, are you truly ready to secure your digital fortune, or are you leaving the door open for the next billion dollar heist?
-
 @ 8bf578f4:b6303c41
2025-06-04 07:20:09
@ 8bf578f4:b6303c41
2025-06-04 07:20:09test
https://nostr.download/6849b84caaa15bdc18ca2e1e1ee00e979c7ecf901787e09054b4bd0196b4ea27.jpg
-
 @ 3a7c74bb:bbdd5960
2025-06-02 11:48:00
@ 3a7c74bb:bbdd5960
2025-06-02 11:48:00- The Foundation (12th Century)
The territory that would become Portugal was originally part of the Kingdom of León and Castile. But in 1128, the young nobleman Afonso Henriques confronted his own mother at the Battle of São Mamede, taking control of the County of Portugal (Condado Portucalense).
In 1139, after winning the Battle of Ourique, he declared himself King of Portugal. Independence was recognized in 1143 by the King of León and confirmed by the Pope in 1179.
- Expansion and the discoveries (14th–16th Centuries)
In the following centuries, Portugal consolidated its territory and set out to sea. The 15th century marked the beginning of the Portuguese Discoveries:
🚢 1419–1420 – Discovery of Madeira and the Azores 🚢 1488 – Bartolomeu Dias rounds the Cape of Good Hope 🚢 1498 – Vasco da Gama reaches India 🚢 1500 – Pedro Álvares Cabral discovers Brazil
During this period, Portugal created a vast maritime empire with colonies in Africa, the Americas, Asia, and Oceania.
- Iberian Union and the restoration (1580–1640)
In 1580, after a dynastic crisis caused by the death of King Sebastian, Portugal came under Spanish rule in what is known as the Iberian Union. For 60 years, the Spanish kings ruled Portugal until, in 1640, a revolt led by John IV restored Portuguese independence.
- The decline of the Empire and the 1755 earthquake
The 18th century was marked by the Lisbon earthquake of 1755, one of the greatest disasters of its time, which destroyed much of the capital. The Marquis of Pombal led the country’s reconstruction and modernization.
The empire began to weaken, culminating in the independence of Brazil in 1822.
- Wars, republic, and dictatorship (19th–20th Centuries)
Portugal faced internal crises and took part in World War I. In 1910, the monarchy fell and the Portuguese Republic was proclaimed.
In the 20th century, the country lived under the Estado Novo dictatorship (1933–1974), led by António de Oliveira Salazar. In 1974, the Carnation Revolution brought democracy, and the following year, the last African colonies gained independence.
- Modern Portugal (21st Century)
In 1986, Portugal joined the European Union, marking a period of growth and modernization. Today, it is a democratic country with a rich culture and a history that continues to inspire the world.
- And what about the islands?
The Autonomous Regions of Madeira and the Azores play a fundamental role in Portuguese identity. Discovered in the 15th century, they have been part of Portugal ever since and have their own regional governments.
Madeira is known for its wine and stunning landscapes, while the Azores are famous for their volcanic nature and unique culture.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite writer from Madeira. Long live freedom!